-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ cefb08d1:f419beff
2025-05-25 07:39:53
@ cefb08d1:f419beff
2025-05-25 07:39:53https://stacker.news/items/988759
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 57c631a3:07529a8e
2025-04-07 13:17:50
@ 57c631a3:07529a8e
2025-04-07 13:17:50What is Growth Engineering? Before we start: if you’ve already filled out the What is your tech stack? survey: thank you! If you’ve not done so, your help will be greatly appreciated. It takes 5-15 minutes to complete. Those filling out will receive results before anyone else, and additional analysis from myself and Elin. Fill out this survey here.**
npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m
Growth engineering was barely known a decade ago, but today, most scaleups and many publicly traded tech companies have dedicated growth teams staffed by growth engineers. However, some software engineers are still suspicious of this new area because of its reputation for hacky code with little to no code coverage.
For this reason and others, I thought it would be interesting to learn more from an expert who can tell us all about the practicalities of this controversial domain. So I turned to Alexey Komissarouk, who’s been in growth engineering since 2016, and was in charge of it at online education platform, MasterClass. These days, Alexey lives in Tokyo, Japan, where he advises on growth engineering and teaches the Growth Engineering course at Reforge.
In today’s deep dive, Alexey covers:
- What is Growth Engineering? In the simplest terms: writing code to help a company make more money. But there are details to consider: like the company size where it makes sense to have a dedicated team do this.
- What do Growth Engineers work on? Business-facing work, empowerment and platform work are the main areas.
- Why Growth Engineers move faster than Product Engineers. Product Engineers ship to build: Growth Engineers ship to learn. Growth Engineers do take shortcuts that would make no sense when building for longevity – doing this on purpose.
- Tech stack. Common programming languages, monitoring and oncall, feature flags and experimentation, product analytics, review apps, and more.
- What makes a good Growth Engineer? Curiosity, “build to learn” mindset and a “Jack of all trades” approach.
- Where do Growth Engineers fit in? Usually part of the engineering department, either operating as with an “owner” or a “hitchiker” model.
- Becoming a Growth Engineer. A great area if you want to eventually become a founder or product manager – but even if not, it can accelerate your career growth. Working in Growth forces you to learn more about the business.
With that, it’s over to Alexey:
I’ll never forget the first time I made my employer a million dollars.
I was running a push notification A/B test for meal delivery startup Sprig, trying to boost repeat orders.
A push notification similar to what we tested to boost repeat orders
Initial results were unpromising; the push notification was not receiving many opens. Still, I wanted to be thorough: before concluding the idea was a failure, I wrote a SQL query to compare order volume for subsequent weeks between customers in test vs control.
The SQL used to figure out the push notification’s efficiency
As it turned out, our test group “beat” the control group by around 10%:
‘review_5_push’ was the new type of push notification. Roughly the same amount of users clicked it, but they placed 10% more in orders
I plugged the numbers into a significance calculator, which showed it was statistically significant – or “stat-sig” – and therefore highly unlikely to be a coincidence. This meant we had a winner on our hands! But how meaningful was it, really, and what would adding the push notification mean for revenue, if rolled out to 100% of users?
It turned out this experiment created an additional $1.5 million dollars, annually, with just one push notification. Wow!
I was hooked. Since that day, I've shipped hundreds of experimental “winners” which generated hundreds of millions of incremental revenue for my employers. But you never forget the first one. Moments like this is what growth engineering is all about.
1. What is Growth Engineering?
Essentially, growth engineering is the writing of code to make a company money. Of course, all code produced by a business on some level serves this purpose, but while Product Engineers focus on creating a Product worth paying for, Growth Engineers instead focus on making that good product have a good business. To this end, they focus on optimizing and refining key parts of the customer journey, such as:
- Getting more people to consider the product
- Converting them into paying customers
- Keeping them as customers for longer, and spending more
What kinds of companies employ Growth Engineers? Places you’ve heard of, like Meta, LinkedIn, DoorDash, Coinbase, and Dropbox, are some of the ones I’ve had students from. There’s also OpenAI, Uber, Tiktok, Tinder, Airbnb, Pinterest… the list of high-profile companies goes on. Most newer public consumer companies you’ve heard have a growth engineering org, too.
Typically, growth engineering orgs are started by companies at Series B stage and beyond, so long as they are selling to either consumers or businesses via SaaS. These are often places trying to grow extremely fast, and have enough software engineers that some can focus purely on growth. Before the Series B stage, a team is unlikely to be ready for growth for various reasons; likely that it hasn’t found product-market fit, or has no available headcount, or lacks the visitor traffic required to run A/B tests.
Cost is a consideration. A fully-loaded growth team consisting of a handful of engineers, a PM, and a designer costs approximately 1 million dollars annually. To justify this, a rule of thumb is to have at least $5 million dollars in recurring revenue – a milestone often achieved at around the Series B stage.
Despite the presence of growth engineering at many public consumer tech companies, the field itself is still quite new, as a discipline and as a proper title.
Brief history of growth engineering
When I joined Opendoor in 2016, there was a head of growth but no dedicated growth engineers, but there were by the time I left in 2020. At MasterClass soon after, there was a growth org and a dozen dedicated growth engineers. So when did growth engineering originate?
The story is that its origins lie at Facebook in 2007. The team was created by then-VP of platform and monetization Chamath Palihapitiya. Reforce founder and CEO Brian Balfour shares:
“Growth (the kind found on an org chart) began at Facebook under the direction of Chamath Palihapitiya. In 2007, he joined the early team in a nebulous role that fell somewhere between Product, Marketing, and Operations. According to his retelling of the story on Recode Decode, after struggling to accomplish anything meaningful in his first year on the job, he was on the verge of being fired.Sheryl Sandberg joined soon after him, and in a hail mary move he pitched her the game-changing idea that led to the creation of the first-ever growth team. This idea not only saved his job, but earned him the lion’s share of the credit for Facebook’s unprecedented growth.At the time, Sheryl and Mark asked him, “What do you call this thing where you help change the product, do some SEO and SEM, and algorithmically do this or that?”His response: “I don’t know, I just call that, like, Growth, you know, we’re going to try to grow. I’ll be the head of growing stuff."And just like that, Growth became a thing.”
Rather than focus on a particular product or feature, the growth team at Facebook focused on moving the needle, and figuring out which features to work on. These days, Meta employs hundreds if not thousands of growth engineers.
2. What do Growth Engineers work on?
Before we jump into concrete examples, let’s identify three primary focus areas that a growth engineer’s work usually involves.
- Business-facing work – improving the business directly
- Empowerment work – enabling other teams to improve the business
- Platform work – improving the velocity of the above activities
Let’s go through all three:
Business-facing work
This is the bread and butter of growth engineering, and follows a common pattern:
- Implement an idea. Try something big or small to try and move a key business metric, which differs by team but is typically related to conversion rate or retention.
- Quantify impact. Usually via A/B testing.
- Analyze impact. Await results, analyze impact, ship or roll back – then go back to the first step.
Experiments can lead to sweeping or barely noticeable changes. A famous “I can’t believe they needed to test this” was when Google figured out which shade of blue generates the most clicks. At MasterClass, we tested things across the spectrum:
- Small: should we show the price right on the homepage, was that a winner? Yes, but we framed it in monthly terms of $15/month, not $180/year.
- Medium: when browsing a course page, should we include related courses, or more details about the course itself? Was it a winner? After lengthy experimentation, it was hard to tell: both are valuable and we needed to strike the right balance.
- Large: when a potential customer is interested, do we take them straight to checkout, or encourage them to learn more? Counterintuitively, adding steps boosted conversion!
Empowerment
One of the best ways an engineer can move a target metric is by removing themselves as a bottleneck, so colleagues from marketing can iterate and optimize freely. To this end, growth engineers can either build internal tools or integrate self-serve MarTech (Marketing Technology) vendors.
With the right tool, there’s a lot that marketers can do without engineering’s involvement:
- Build and iterate on landing pages (Unbounce, Instapage, etc)
- Draft and send email, SMS and Push Notifications (Iterable, Braze, Customer.io, etc)
- Connect new advertising partners (Google Tag Manager, Segment, etc)
We go more into detail about benefits and applications in the MarTech section of Tech Stack, below.
Platform work
As a business scales, dedicated platform teams help improve stability and velocity for the teams they support. Within growth, this often includes initiatives like:
- Experiment Platform. Many parts of running an experiment can be standardized, from filtering the audience, to bucketing users properly, to observing statistical methodology. Historically, companies built reusable Experiment Platforms in-house, but more recently, vendors such as Eppo and Statsig have grown in popularity with fancy statistical methodologies like “Controlled Using Pre-Experiment Data” (CUPED) that give more signal with less data.
- Reusable components. Companies with standard front-end components for things like headlines, buttons, and images, dramatically reduce the time required to spin up a new page. No more "did you want 5 or 6 pixels here" with a designer; instead growth engineers rely on tools like Storybook to standardize and share reusable React components.
- Monitoring. Growth engineering benefits greatly from leveraging monitoring to compensate for reduced code coverage. High-quality business metric monitoring tools can detect bugs before they cause damage.
When I worked at MasterClass, having monitoring at the ad layer prevented at least one six-figure incident. One Friday, a marketer accidentally broadened the audience for a particular ad from US-only, to worldwide. In response, the Facebook Ad algorithm went on a spending spree, bringing in plenty of visitors from places like Brazil and India, whom we knew from past experience were unlikely to purchase the product. Fortunately, our monitoring noticed the low-performing campaign within minutes, and an alert was sent to the growth engineer on-call, who immediately reached out to the marketer and confirmed the change was unintentional, and then shut down the campaign.
Without this monitoring, a subtle targeting error like this could have gone unnoticed all weekend and would have eaten up $100,000+ of marketing budget. This episode shows that platform investment can benefit everyone; and since growth needs them most, it’s often the growth platform engineering team which implements them.
As the day-to-day work of a Growth Engineer shows, A/B tests are a critical tool to both measure success and learn. It’s a numbers game: the more A/B tests a team can run in a given quarter, the more of them will end up winners, making the team successful. It’s no wonder, then, that Growth Engineering will pull out all the stops to improve velocity.
3. Why Growth Engineers move faster than Product Engineers
On the surface, growth engineering teams look like product engineering ones; writing code, shipping pull requests, monitoring on-call, etc. So how do they move so much faster? The big reason lies in philosophy and focus, not technology. To quote Elena Verna, head of growth at Dropbox:
“Product Engineering teams ship to build; Growth Engineering teams ship to learn.”
Real-world case: price changes at Masterclass
A few years ago at MasterClass, the growth team wanted to see if changing our pricing model to multiple tiers would improve revenue.
Inspired in part by multiple pricing tiers for competitors such as Netflix (above), Disney Plus, and Hulu.
The “multiple pricing tier” proposal for MasterClass.
From a software engineering perspective, this was a highly complex project because:
- Backend engineering work: the backend did not yet support multiple pricing options, requiring a decent amount of engineering, and rigorous testing to make sure existing customers weren’t affected.
- Client app changes: on the device side, multiple platforms (iOS, iPad, Android, Roku, Apple TV, etc) would each need to be updated, including each relevant app store.
The software engineering team estimated that becoming a “multi-pricing-tier” company would take months across numerous engineering teams, and engineering leadership was unwilling to greenlight that significant investment.
We in growth engineering took this as a challenge. As usual, our goal was not just to add the new pricing model, but to learn how much money it might bring in. The approach we ended up proposing was a Fake Door test, which involves offering a not-yet-available option to customers to gauge interest level. This was risky, as taking a customer who’s ready to pay and telling them to join some kind of waiting list is a colossal waste, and risks making them feel like the target of a “bait and switch” trick.
We found a way. The key insight was that people are only offended about a “bait and switch”, if the “switch” is worse than the “bait.” Telling customers they would pay $100 and then switching to $150 would cause a riot, but starting at $150 and then saying “just kidding, it’s only $100” is a pleasant surprise.
The good kind of surprise.
So long as every test “pricing tier” is less appealing – higher prices, fewer features – than the current offering, we could “upgrade” customers after their initial selection. A customer choosing the cheapest tier gets extra features at no extra cost, while a customer choosing a more expensive tier is offered a discount.
We created three new tiers, at different prices. The new “premium” tier would describe the existing, original offering. Regardless of what potential customers selected, they got this “original offering,” during the experiment.
The best thing about this was that no backend changes were required. There were no real, new, back-end pricing plans; everybody ended up purchasing the same version of MasterClass for the same price, with the same features. The entirety of the engineering work was on building a new pricing page, and the “congratulations, you’ve been upgraded” popup. This took just a few days.
Within a couple of weeks, we had enough data to be confident the financial upside of moving to a multi-pricing-tier model would be significant. With this, we’re able to convince the rest of engineering’s leadership to invest in building the feature properly. In the end, launching multiple pricing tiers turned out to be one of the biggest revenue wins of the year.
Building a skyscraper vs building a tent
The MasterClass example demonstrates the spirit of growth engineering; focusing on building to learn, instead of building to last. Consider building skyscrapers versus tents.
Building a tent optimizes for speed of set-up and tear-down over longevity. You don’t think of a tent as one that is shoddy or low-quality compared to skyscrapers: it’s not even the same category of buildings! Growth engineers maximize use of lightweight materials. To stick with the tents vs skyscraper metaphor: we prioritize lightweight fabric materials over steel and concrete whenever possible. We only resort to traditional building materials when there’s no other choice, or when a direction is confirmed as correct. Quality is important – after all, a tent must keep out rain and mosquitoes. However, the speed-vs-durability tradeoff decision results in very different approaches and outcomes.
4. Tech stack
At first glance, growth and product engineers use the same tooling, and contribute to the same codebases. But growth engineering tends to be high-velocity, experiment-heavy, and with limited test coverage. This means that certain “nice to have” tools for product engineering are mission-critical for growth engineers.
Read more https://connect-test.layer3.press/articles/ea02c1a1-7cfa-42b4-8722-0165abcae8bb
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 8d34bd24:414be32b
2025-05-25 06:29:21
@ 8d34bd24:414be32b
2025-05-25 06:29:21It seems like most Christians today have lost their reverence and awe of God. We’ve attributed God’s awesome creation by the word of His mouth to random chance and a Big Bang. We’ve attributed the many layers of sediment to millions and billions of years of time instead of God’s judgment of evil. We’ve emphasized His love and mercy to the point that we’ve forgotten about His holiness and righteous wrath. We’ve brought God down to our level and made Him either our “buddy” or made Him our magic genie servant, who is just there to answer our every want and whim.
The God of the Bible is a holy and awesome God who should be both loved and feared.
The fear of the Lord is the beginning of knowledge;\ Fools despise wisdom and instruction. (Proverbs 1:7)
The God of the Bible is the Lord of Lords and King of Kings who “… upholds all things by the word of His power. …” (Hebrews 1:3). Yes, God loves us as sons. Yes, God is merciful. Yes, through Jesus we have the blessed opportunity to approach God directly. None of that means we get to treat God like just another friend. We are to approach God with fear and trembling and worship Him in reverence and awe.
Worship the Lord with reverence And rejoice with trembling. (Psalm 2:11)
Part of the problem is that our culture just doesn’t show reverence to authority. It focuses on self and freedom. The whole thought of reverence for authority is incomprehensible for many. Look at this Psalm of worship:
The Lord reigns, let the peoples tremble;\ He is enthroned above the cherubim, let the earth shake!\ The Lord is great in Zion,\ And He is exalted above all the peoples.\ Let them praise Your great and awesome name;\ Holy is He. (Psalm 99:1-3)
This is the way we should view God and the proper attitude for approaching God.
Another issue is that we don’t study what God has done in the past. In the Old Testament, God commanded the Israelites to setup monuments of remembrance and to teach their kids all of the great things God had done for them. When they failed to do so, Israel drifted astray.
You shall teach them to your sons, talking of them when you sit in your house and when you walk along the road and when you lie down and when you rise up. (Deuteronomy 11:19)
God has given us the Bible, His word, so that we can know Him, know His character, and know His great deeds. When we fail to be in His word daily, we can forget (or not even know) the greatness of our God.
Establish Your word to Your servant,\ As that which produces reverence for You. (Psalm 119:38)
Do you love God’s word like this? Do you hunger for God’s word? Do you seek to know everything about God that you can know? When we love someone or something, we want to know everything about it.
Princes persecute me without cause,\ But my heart stands in awe of Your words.\ **I rejoice at Your word,\ As one who finds great spoil. \ (Psalm 119:161-162) {emphasis mine}
In addition to what we can learn about God in the Bible, we also need to remember what God has done in our own lives. We need to dwell on what God has done for us. We can just try to remember. Even better (I’ll admit this is a weakness for me), write down answered prayers, blessings, and other things God has done for you. My son has been writing down one blessing every day for over a year. What an example he is!
After we have thought about what God has done for us and those we care about, we should praise Him for His great works.
Shout joyfully to God, all the earth;\ Sing the glory of His name;\ Make His praise glorious.\ Say to God, “How awesome are Your works!\ Because of the greatness of Your power \ Your enemies will give feigned obedience to You.\ All the earth will worship You,\ And will sing praises to You;\ They will sing praises to Your name.” Selah.\ **Come and see the works of God,\ Who is awesome in His deeds toward the sons of men. \ (Psalm 66:1-5) {emphasis mine}
There is nothing we can do to earn salvation from God, but we should be in awe of what He has done for us leading to submission and obedience in gratitude.
Therefore, since we receive a kingdom which cannot be shaken, let us show gratitude, by which we may offer to God an acceptable service with reverence and awe; for our God is a consuming fire. (Hebrews 12:28-29) {emphasis mine}
Are you thankful for your blessings or resentful for what you don’t have? Do you worship God or take things He has provided for granted? Do you tell the world the awesome things God has done for you or do you stay silent? Do you claim to be a Christian, but live a life no different than those around you?
Then the Lord said,
“Because this people draw near with their words\ And honor Me with their lip service,\ But they remove their hearts far from Me,\ And their reverence for Me consists of tradition learned by rote, (Isaiah 29:13)
I hope this passage does not describe your relation ship with our awesome God. He deserves so much more. Instead we should be zealous to praise God and share His goodness with those around us.
Who is there to harm you if you prove zealous for what is good? But even if you should suffer for the sake of righteousness, you are blessed. And do not fear their intimidation, and do not be troubled, but sanctify Christ as Lord in your hearts, always being ready to make a defense to everyone who asks you to give an account for the hope that is in you, yet with gentleness and reverence; (1 Peter 3:13-15) {emphasis mine}
Did you know that you can even show reverence by your every day work?
By faith Noah, being warned by God about things not yet seen, in reverence prepared an ark for the salvation of his household, by which he condemned the world, and became an heir of the righteousness which is according to faith. (Hebrews 11:7) {emphasis mine}
When Noah stepped out in faith and obedience to God and built the ark as God commanded, despite the fact that the people around him probably thought he was crazy building a boat on dry ground that had never flooded, his work was a kind of reverence to God. Are there areas in your life where you can obey God in reverence to His awesomeness? Do you realize that quality work in obedience to God can be a form of worship?
Just going above and beyond in your job can be a form of worship of God if you are working extra hard to honor Him. Obedience is another form of worship and reverence.
Then Zerubbabel the son of Shealtiel, and Joshua the son of Jehozadak, the high priest, with all the remnant of the people, obeyed the voice of the Lord their God and the words of Haggai the prophet, as the Lord their God had sent him. And the people showed reverence for the Lord. (Haggai 1:12) {emphasis mine}
Too many people have put the word of men (especially scientists) above the word of God and have tried to change the clear meaning of the Bible. I used to think it strange how the Bible goes through the days of creation and ends each day with “and there was evening and there was morning, the xth day.” Since a day has an evening and a morning, that seemed redundant. Why did God speak in this manner? God knew that a day would come when many scientist would try to disprove God and would claim that these days were not 24 hour days, but long ages. When a writer is trying to convey long ages, the writer does not mention evening/morning and doesn’t count the days.1
When we no longer see God as speaking the universe and everything in it into existence, we tend to not see God as an awesome God. We don’t see His power. We don’t see His knowledge. We don’t see His goodness. We also don’t see His authority. Why do we have to obey God? Because He created us and because He upholds us. Without Him we would not exist. Our creator has the authority to command His creation. When we compromise in this area, we lose our submission, our awe, and our reverence. (For more on the subject see my series.) When we believe His great works, especially those spoken of in Genesis 1-11 and in Exodus, we can’t help but be in awe of our God.
For the word of the Lord is upright,\ And all His work is done in faithfulness.\ He loves righteousness and justice;\ The earth is full of the lovingkindness of the Lord.\ By the word of the Lord the heavens were made,\ And by the breath of His mouth all their host.\ He gathers the waters of the sea together as a heap;\ He lays up the deeps in storehouses.\ **Let all the earth fear the Lord;\ Let all the inhabitants of the world stand in awe of Him. \ (Psalm 33:4-8) {emphasis mine}
Remembering God’s great works, we can’t help but worship in awe and reverence.
By awesome deeds You answer us in righteousness, O God of our salvation,\ *You who are the trust of all the ends of the earth* and of the farthest sea;\ Who establishes the mountains by His strength,\ Being girded with might;\ Who stills the roaring of the seas,\ The roaring of their waves,\ And the tumult of the peoples.\ They who dwell in the ends of the earth stand in awe of Your signs;\ You make the dawn and the sunset shout for joy. \ (Psalm 65:5-8) {emphasis mine}
If we truly do have awe and reverence for our God, we should be emboldened to tell those around us of His great works.
I will tell of Your name to my brethren;\ In the midst of the assembly I will praise You.\ You who fear the Lord, praise Him;\ All you descendants of Jacob, glorify Him,\ And stand in awe of Him, all you descendants of Israel. \ (Psalm 22:22-23) {emphasis mine}
May God grant you the wisdom to see His awesomeness and to trust Him, serve Him, obey Him, and worship Him as He so rightly deserves. May you always have a right view of God and a hunger for His word and a personal relationship with Him. To God be the Glory!
Trust Jesus
FYI, these are a few more passages on the subject that are helpful, but didn’t fit in the flow of my post.
Great is the Lord, and highly to be praised,\ And His greatness is unsearchable.\ One generation shall praise Your works to another,\ And shall declare Your mighty acts.\ On the glorious splendor of Your majesty\ And on Your wonderful works, I will meditate.\ Men shall speak of the power of Your awesome acts,\ And I will tell of Your greatness. (Psalm 145:3-6)
The boastful shall not stand before Your eyes;\ You hate all who do iniquity.\ You destroy those who speak falsehood;\ The Lord abhors the man of bloodshed and deceit.\ But as for me, by Your abundant lovingkindness I will enter Your house,\ At Your holy temple I will bow in reverence for You. (Psalm 5:5-7) {emphasis mine}
If you do not listen, and if you do not take it to heart to give honor to My name,” says the Lord of hosts, “then I will send the curse upon you and I will curse your blessings; and indeed, I have cursed them already, because you are not taking it to heart. Behold, I am going to rebuke your offspring, and I will spread refuse on your faces, the refuse of your feasts; and you will be taken away with it. Then you will know that I have sent this commandment to you, that My covenant may continue with Levi,” says the Lord of hosts. “My covenant with him was one of life and peace, and I gave them to him as an object of reverence; so he revered Me and stood in awe of My name. (Malachi 2:2-5) {emphasis mine}
-
 @ 04c915da:3dfbecc9
2025-03-10 23:31:30
@ 04c915da:3dfbecc9
2025-03-10 23:31:30Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Usually stolen bitcoin for the reserve creates a perverse incentive. If governments see a bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 6389be64:ef439d32
2025-05-24 21:51:47
@ 6389be64:ef439d32
2025-05-24 21:51:47Most nematodes are beneficial and "graze" on black vine weevil, currant borer moth, fungus gnats, other weevils, scarabs, cutworms, webworms, billbugs, mole crickets, termites, peach tree borer and carpenter worm moths.
They also predate bacteria, recycling nutrients back into the soil and by doing so stimulates bacterial activity. They act as microbial taxis by transporting microbes to new locations of soil as they move through it while providing aeration.
https://stacker.news/items/988573
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-23 13:46:21
@ 5d4b6c8d:8a1c1ee3
2025-05-23 13:46:21You'd think I'd be most excited to talk about that awesome Pacers game, but, no. What I'm most excited about this week is that @grayruby wants to continue Beefing with Cowherd.
Still, I am excited to talk about Tyrese Haliburton becoming a legendary Knicks antagonist. Unfortunately, the Western Conference Finals are not as exciting. Also, why was the MVP announcement so dumb?
The T20k cricket contest is tightening up, as we head towards the finish. Can @Coinsreporter hold on to his vanishing lead?
@Carresan has launched Football Madness. Let's see if we understand whatever the hell this is any better than we did last week.
On this week's Blok'd Shots, we'll ridicule Canada for their disgraceful loss in the World Championships and talk about the very dominant American Florida Panthers, who are favorites to win the Stanley Cup.
Are the Colorado the worst team in MLB history?
The Tush Push has survived another season. Will the NFL eventually ban it or will teams adjust?
Plus, whatever else Stackers want to talk about.
https://stacker.news/items/987399
-
 @ 04c915da:3dfbecc9
2025-03-04 17:00:18
@ 04c915da:3dfbecc9
2025-03-04 17:00:18This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 21335073:a244b1ad
2025-05-21 16:58:36
@ 21335073:a244b1ad
2025-05-21 16:58:36The other day, I had the privilege of sitting down with one of my favorite living artists. Our conversation was so captivating that I felt compelled to share it. I’m leaving his name out for privacy.
Since our last meeting, I’d watched a documentary about his life, one he’d helped create. I told him how much I admired his openness in it. There’s something strange about knowing intimate details of someone’s life when they know so little about yours—it’s almost like I knew him too well for the kind of relationship we have.
He paused, then said quietly, with a shy grin, that watching the documentary made him realize how “odd and eccentric” he is. I laughed and told him he’s probably the sanest person I know. Because he’s lived fully, chasing love, passion, and purpose with hardly any regrets. He’s truly lived.
Today, I turn 44, and I’ll admit I’m a bit eccentric myself. I think I came into the world this way. I’ve made mistakes along the way, but I carry few regrets. Every misstep taught me something. And as I age, I’m not interested in blending in with the world—I’ll probably just lean further into my own brand of “weird.” I want to live life to the brim. The older I get, the more I see that the “normal” folks often seem less grounded than the eccentric artists who dare to live boldly. Life’s too short to just exist, actually live.
I’m not saying to be strange just for the sake of it. But I’ve seen what the crowd celebrates, and I’m not impressed. Forge your own path, even if it feels lonely or unpopular at times.
It’s easy to scroll through the news and feel discouraged. But actually, this is one of the most incredible times to be alive! I wake up every day grateful to be here, now. The future is bursting with possibility—I can feel it.
So, to my fellow weirdos on nostr: stay bold. Keep dreaming, keep pushing, no matter what’s trending. Stay wild enough to believe in a free internet for all. Freedom is radical—hold it tight. Live with the soul of an artist and the grit of a fighter. Thanks for inspiring me and so many others to keep hoping. Thank you all for making the last year of my life so special.
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-24 15:06:32
@ 5d4b6c8d:8a1c1ee3
2025-05-24 15:06:32I was just updating our potential points, now that we know who won MVP, who made All NBA 1st team, and which teams are still alive for the title, and it turns out that no matter who wins the title @gnilma will win this contest.
Congratulations, @gnilma!
This is just further proof that @gnilma is our NBA Guru.
Let me know where you want your 7k in winnings sent.
https://stacker.news/items/988245
-
 @ 04c915da:3dfbecc9
2025-02-25 03:55:08
@ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 6a6be47b:3e74e3e1
2025-05-24 08:21:35
@ 6a6be47b:3e74e3e1
2025-05-24 08:21:35Hi, frens!
🥳 This is my first post over here, yaaay! I’m very excited to start this journey. I have lots of posts on my website https://samhainsam.art/ , but I decided to give you a short introduction to me and my artwork. Shall we?
But first, how’s your weekend going? Already dreading Monday, or just enjoying the moment? I hope it’s the latter, but if not, that’s okay too. Everything passes, and while that might not be the most comforting thought, knowing that it will eventually pass—and, most importantly, that we get to decide how to respond—makes a big difference. Either way, we’re all going to die, so take it as you wish! 😅
Anyway, I wanted to share a little something. If you’ve visited my shop on Ko-fi https://ko-fi.com/samhainsam/shop , you might have wondered why it seems a bit all over the place. Or maybe you haven’t noticed or don’t care—but either way, I thought I’d clarify.
🖼️ I’m a self-taught artist who loves everything related to religion, occultism, paganism, animals, and esotericism—and how all these themes intertwine in our lives. I paint and illustrate inspired by these ideas.
Most of my recent paintings come with a blog post explaining their background. Even before, I always researched the subjects I painted, but lately, I’ve been diving much deeper.
🎨 My “Wheel of the Year” series has completely fascinated me. I’ve been learning so many nuggets of wisdom, and discovering how Christianity borrowed or even erased many symbols and traditions to create new narratives. For example, Imbolc was rebranded as Candlemas, and my blog post about the Spanish Inquisition touches on some of these symbols and their impact on both past and present society.
🐦 I also have some paintings just about birds—I'm a bit of a sucker for them! Shoebills and cassowaries are among my favorites, and I might end up painting them again soon. But you get the picture! If not, why not take a peek at my blog? https://samhainsam.art/blog/
🖋️ You can read something fun and interesting while enjoying my artwork.
Come on over, and let’s have some cool and healthy fun.
Enjoy your weekend, my friends!
Godspeed ⚡
https://stacker.news/items/988069
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ 06830f6c:34da40c5
2025-05-24 04:21:03
@ 06830f6c:34da40c5
2025-05-24 04:21:03The evolution of development environments is incredibly rich and complex and reflects a continuous drive towards greater efficiency, consistency, isolation, and collaboration. It's a story of abstracting away complexity and standardizing workflows.
Phase 1: The Bare Metal & Manual Era (Early 1970s - Late 1990s)
-
Direct OS Interaction / Bare Metal Development:
- Description: Developers worked directly on the operating system's command line or a basic text editor. Installation of compilers, interpreters, and libraries was a manual, often arcane process involving downloading archives, compiling from source, and setting environment variables. "Configuration drift" (differences between developer machines) was the norm.
- Tools: Text editors (Vi, Emacs), command-line compilers (GCC), Makefiles.
- Challenges: Extremely high setup time, dependency hell, "works on my machine" syndrome, difficult onboarding for new developers, lack of reproducibility. Version control was primitive (e.g., RCS, SCCS).
-
Integrated Development Environments (IDEs) - Initial Emergence:
- Description: Early IDEs (like Turbo Pascal, Microsoft Visual Basic) began to integrate editors, compilers, debuggers, and sometimes GUI builders into a single application. This was a massive leap in developer convenience.
- Tools: Turbo Pascal, Visual Basic, early Visual Studio versions.
- Advancement: Improved developer productivity, streamlined common tasks. Still relied on local system dependencies.
Phase 2: Towards Dependency Management & Local Reproducibility (Late 1990s - Mid-2000s)
-
Basic Build Tools & Dependency Resolvers (Pre-Package Managers):
- Description: As projects grew, manual dependency tracking became impossible. Tools like Ant (Java) and early versions of
autoconf/makefor C/C++ helped automate the compilation and linking process, managing some dependencies. - Tools: Apache Ant, GNU Autotools.
- Advancement: Automated build processes, rudimentary dependency linking. Still not comprehensive environment management.
- Description: As projects grew, manual dependency tracking became impossible. Tools like Ant (Java) and early versions of
-
Language-Specific Package Managers:
- Description: A significant leap was the emergence of language-specific package managers that could fetch, install, and manage libraries and frameworks declared in a project's manifest file. Examples include Maven (Java), npm (Node.js), pip (Python), RubyGems (Ruby), Composer (PHP).
- Tools: Maven, npm, pip, RubyGems, Composer.
- Advancement: Dramatically simplified dependency resolution, improved intra-project reproducibility.
- Limitation: Managed language-level dependencies, but not system-level dependencies or the underlying OS environment. Conflicts between projects on the same machine (e.g., Project A needs Python 2.7, Project B needs Python 3.9) were common.
Phase 3: Environment Isolation & Portability (Mid-2000s - Early 2010s)
-
Virtual Machines (VMs) for Development:
- Description: To address the "it works on my machine" problem stemming from OS-level and system-level differences, developers started using VMs. Tools like VMware Workstation, VirtualBox, and later Vagrant (which automated VM provisioning) allowed developers to encapsulate an entire OS and its dependencies for a project.
- Tools: VMware, VirtualBox, Vagrant.
- Advancement: Achieved strong isolation and environment reproducibility (a true "single environment" for a project).
- Limitations: Resource-heavy (each VM consumed significant CPU, RAM, disk space), slow to provision and boot, difficult to share large VM images.
-
Early Automation & Provisioning Tools:
- Description: Alongside VMs, configuration management tools started being used to automate environment setup within VMs or on servers. This helped define environments as code, making them more consistent.
- Tools: Chef, Puppet, Ansible.
- Advancement: Automated provisioning, leading to more consistent environments, often used in conjunction with VMs.
Phase 4: The Container Revolution & Orchestration (Early 2010s - Present)
-
Containerization (Docker):
- Description: Docker popularized Linux Containers (LXC), offering a lightweight, portable, and efficient alternative to VMs. Containers package an application and all its dependencies into a self-contained unit that shares the host OS kernel. This drastically reduced resource overhead and startup times compared to VMs.
- Tools: Docker.
- Advancement: Unprecedented consistency from development to production (Dev/Prod Parity), rapid provisioning, highly efficient resource use. Became the de-facto standard for packaging applications.
-
Container Orchestration:
- Description: As microservices and container adoption grew, managing hundreds or thousands of containers became a new challenge. Orchestration platforms automated the deployment, scaling, healing, and networking of containers across clusters of machines.
- Tools: Kubernetes, Docker Swarm, Apache Mesos.
- Advancement: Enabled scalable, resilient, and complex distributed systems development and deployment. The "environment" started encompassing the entire cluster.
Phase 5: Cloud-Native, Serverless & Intelligent Environments (Present - Future)
-
Cloud-Native Development:
- Description: Leveraging cloud services (managed databases, message queues, serverless functions) directly within the development workflow. Developers focus on application logic, offloading infrastructure management to cloud providers. Containers become a key deployment unit in this paradigm.
- Tools: AWS Lambda, Azure Functions, Google Cloud Run, cloud-managed databases.
- Advancement: Reduced operational overhead, increased focus on business logic, highly scalable deployments.
-
Remote Development & Cloud-Based IDEs:
- Description: The full development environment (editor, terminal, debugger, code) can now reside in the cloud, accessed via a thin client or web browser. This means developers can work from any device, anywhere, with powerful cloud resources backing their environment.
- Tools: GitHub Codespaces, Gitpod, AWS Cloud9, VS Code Remote Development.
- Advancement: Instant onboarding, consistent remote environments, access to high-spec machines regardless of local hardware, enhanced security.
-
Declarative & AI-Assisted Environments (The Near Future):
- Description: Development environments will become even more declarative, where developers specify what they need, and AI/automation tools provision and maintain it. AI will proactively identify dependency issues, optimize resource usage, suggest code snippets, and perform automated testing within the environment.
- Tools: Next-gen dev container specifications, AI agents integrated into IDEs and CI/CD pipelines.
- Prediction: Near-zero environment setup time, self-healing environments, proactive problem identification, truly seamless collaboration.
web3 #computing #cloud #devstr
-
-
 @ 51bbb15e:b77a2290
2025-05-21 00:24:36
@ 51bbb15e:b77a2290
2025-05-21 00:24:36Yeah, I’m sure everything in the file is legit. 👍 Let’s review the guard witness testimony…Oh wait, they weren’t at their posts despite 24/7 survellience instructions after another Epstein “suicide” attempt two weeks earlier. Well, at least the video of the suicide is in the file? Oh wait, a techical glitch. Damn those coincidences!
At this point, the Trump administration has zero credibility with me on anything related to the Epstein case and his clients. I still suspect the administration is using the Epstein files as leverage to keep a lot of RINOs in line, whereas they’d be sabotaging his agenda at every turn otherwise. However, I just don’t believe in ends-justify-the-means thinking. It’s led almost all of DC to toss out every bit of the values they might once have had.
-
 @ 0fa80bd3:ea7325de
2025-02-14 23:24:37
@ 0fa80bd3:ea7325de
2025-02-14 23:24:37intro
The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises.
In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously.
I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea.
It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope.
After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes.
I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project.
With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed.
With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation.
At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
-
 @ c9badfea:610f861a
2025-05-20 19:49:20
@ c9badfea:610f861a
2025-05-20 19:49:20- Install Sky Map (it's free and open source)
- Launch the app and tap Accept, then tap OK
- When asked to access the device's location, tap While Using The App
- Tap somewhere on the screen to activate the menu, then tap ⁝ and select Settings
- Disable Send Usage Statistics
- Return to the main screen and enjoy stargazing!
ℹ️ Use the 🔍 icon in the upper toolbar to search for a specific celestial body, or tap the 👁️ icon to activate night mode
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-23 23:37:17
@ 5d4b6c8d:8a1c1ee3
2025-05-23 23:37:17@grayruby loves to blow up the odds of various sports markets at Predyx. Well, the jig is up, because I finally managed to deposit some sats at BetPlay where I can leverage the mismatched odds.
So, I've now locked in guaranteed wins on the 49ers winning the Super Bowl and the Panthers winning the Stanley Cup.
https://stacker.news/items/987847
-
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 58537364:705b4b85
2025-05-25 15:38:04
@ 58537364:705b4b85
2025-05-25 15:38:04พระอาจารย์ไพศาล วิสาโล วัดป่าสุคะโต แสดงธรรมเย็นวันที่ 28 กันยายน 2565

ที่ประเทศจีนเมื่อสัก 100 - 200 ปีก่อน ชายคนหนึ่งตาบอด แต่ก็สามารถใช้ชีวิตได้ตามปกติ วันหนึ่งก็เดินไปเยี่ยมเพื่อน ซึ่งอยู่ในเมืองเดียวกัน แต่ก็เดินไกลสักหน่อย แล้วชายตาบอดคนนี้ก็เดินได้โดยที่ไม่ต้องใช้ไม้เท้า ถึงบ้านเพื่อนก็สนทนากับเพื่อนหลายเรื่องหลายราว คุยกันถูกคอ จนกระทั่งค่ำ ก็ได้เวลาที่ชายตาบอดจะกลับบ้าน แต่ก่อนที่แกจะเดินออกจากบ้าน เพื่อนก็ยื่นโคมให้ โคมนี่เป็นคนที่จุดไฟให้แสงสว่างในเวลากลางคืน
ชายตาบอดก็บอกว่าฉันไม่ต้องใช้โคมหรอก เดินได้โดยที่ไม่เห็นอะไร ไม่ต้องใช้แสงสว่างก็เดินได้ ทางเส้นนี้ฉันก็คุ้นแล้ว เพื่อนก็บอกว่าที่ให้โคมนี่ ก็เพื่อเวลาคุณเดินกลับบ้านตามตรอกซอกซอย มันจะได้ให้แสงสว่าง คนที่เขาเดินสวนคุณมา เขาเห็นทาง เขาก็จะได้ไม่เดินชนคุณไงล่ะ เหตุผลนี้ก็ทำให้ชายตาบอดถือโคมกลับบ้าน ทั้งๆ ที่ตัวเองไม่จำเป็นต้องใช้โคมนั้นเลย
ระหว่างที่เดินกลับบ้านก็มีคนหลายคนเดินสวน เพราะมันเป็นตรอกซอกซอยที่มีคนเดินผ่านไปผ่านมาอยู่ แต่ว่าพอเดินมาพักหนึ่ง ปรากฏว่ามีผู้ชายคนหนึ่งเดินชนชายตาบอดอย่างแรงเลย จนล้มเลย ชายตาบอดก็โกรธมาก ก็พูดขึ้นมาว่าแกตาบอดหรือไง แกไม่เห็นหรือโคมที่ฉันถือนี่ ชายคนที่เดินชนชายตาบอดก็บอกว่าขอโทษครับ ขอโทษจริงๆ แต่โคมที่พี่จุดนี่มันดับไปนานแล้วนะ เรื่องก็จบเท่านี้นะ ฟังแล้วเราได้แง่คิดอะไรไหม
เรื่องนี้อาจจะเป็นนิทานนะ แต่มันไม่ใช่นิทานประเภทว่าสอน บอกเราในตอนท้ายว่านิทานเรื่องนี้สอนอะไร แต่ว่ามันจบลงโดยให้เราคิดเอง ฟังเรื่องนี้แล้วเราได้แง่คิดอะไร
แง่คิดอย่างหนึ่งก็คือว่าในการดำเนินชีวิตของคนเรา เราควรจะคิดถึงคนอื่นด้วย ของบางอย่างเราไม่จำเป็น แต่ว่ามันมีประโยชน์กับคนอื่น ถ้าเรานึกถึงคนอื่น มันก็ไม่ใช่ประโยชน์กับคนอื่นอย่างเดียว มันเป็นประโยชน์กับเราด้วย อย่างชายตาบอด เขาไม่จำเป็นต้องใช้โคมเลย ในการเดินกลับบ้านยามค่ำคืน แต่เพื่อนคะยั้นคะยอให้ถือโคมเพื่ออะไร ก็เพื่อประโยชน์ของคนอื่นที่เขาตาดี แล้วเขาต้องใช้แสงสว่างในการเดินสัญจร
การที่ชายตาบอดถือโคม ไม่ได้เพื่อประโยชน์ของตัวเอง แต่เพื่อประโยชน์ของคนอื่น แต่สุดท้ายมันก็เป็นประโยชน์กับตัวเอง เพราะถ้าหากว่าคนที่เขาเดินสวนมา เขาเห็นชายตาบอดถือโคม เขาก็ไม่เดินชน ฉะนั้นทีแรกชายตาบอดก็เดินได้สะดวกสบาย ไม่มีใครชน ก็เพราะว่าคนอื่นเขาเห็นแสงสว่างจากโคมนั้น
อันนี้เขาสอนว่าคนเราควรจะนึกถึงผู้อื่น ของบางอย่างแม้เราไม่จำเป็น แต่ว่ามันเป็นประโยชน์กับผู้อื่นก็ควรทำ หรือบางอย่างอาจจะไม่สะดวกกับเรา แต่ว่ามันช่วยคนอื่นได้ อย่างเช่นการถือโคม มันคงไม่สะดวกสบายเท่ากับเดินตัวเปล่า แต่ว่าเมื่อเดินถือโคมแล้ว มันก็เป็นประโยชน์กับคนที่เดินสวนมาด้วย แต่สุดท้ายมันก็กลับมาเป็นประโยชน์กับชายตาบอดนั่นเอง อย่างที่พูดไปแล้ว ไม่มีใครมาเดินชน
ในชีวิตของคนเรา เราควรจะคิดถึงคนอื่น ฉะนั้นการที่สังคมหรือบ้านเมืองมันน่าอยู่ ก็เพราะผู้คนไม่ได้คิดถึงแต่ตัวเองอย่างเดียว การกระทำบางอย่าง เราทำเพื่อประโยชน์ของส่วนรวม เพื่อผู้อื่น ยกตัวอย่างง่ายๆ เวลาเรากินอะไร มันมีขยะอยู่ในมือ จะเป็นถุงพลาสติก จะเป็นนมกล่อง หรือจะเป็นขวด ขวดน้ำที่กลายเป็นขยะเรียบร้อยแล้ว ทำไมเราควรจะถือขยะนั้นไว้กับตัว จนกว่าจะเห็นถังขยะจึงหย่อนลงถังขยะ
ที่จริงถ้าเรานึกถึงแต่ตัวเอง เราก็แค่โยนมันทิ้งขยะนั้นข้างทาง สบายดีนะ หลายคนก็ทำอย่างนั้น คนเราถ้าคิดถึงแต่ตัวเอง เราไม่เก็บมันไว้กับตัว แล้วก็รอจนกว่าจะเดินเห็นถังขยะ แต่คนจำนวนมากเขาก็เก็บขยะเอาไว้ เพื่อที่จะไปทิ้งลงในถังขยะ
อันนี้เพราะอะไร เพราะนึกถึงผู้อื่น นึกถึงคนที่เก็บขยะบ้าง หรือนึกถึงสังคมส่วนรวม ว่าถ้าเราทิ้งขยะไม่เป็นที่ มันก็จะเลอะเทอะ ไม่น่าดู บางคนก็คิดถึงพนักงานเก็บขยะ หรือคิดถึงพนักงานทำความสะอาด ก็เลยช่วยเขาด้วยการทิ้งขยะเป็นที่ ทั้งที่ถ้าทิ้งข้างทาง กินเสร็จ ดื่มน้ำเสร็จ ดูดนมกล่องเสร็จ ทิ้งไปเลยนี่มันสบายกว่า แต่เป็นเพราะเราคิดถึงคนอื่น เราจึงเอาไปทิ้งเป็นที่
หรือการปิดไฟ บางทีเราก็เห็นไฟเปิดอยู่ที่ห้องน้ำ หรือที่ห้องที่โล่ง เราก็อุตส่าห์เดินไป แทนที่เราจะกลับบ้านเลย เราก็เดินไปที่ห้องน้ำเพื่อที่จะปิดสวิตช์ไฟ เรายอมเสียเวลาเพื่ออะไร ก็เพื่อส่วนรวม หรืออาจจะเป็นเพราะว่าเราอยากจะช่วยพนักงานที่เขาดูแลสถานที่นั้น ไม่ต้องเหนื่อยกับการวิ่งการเดินตามปิดไฟ ที่วัดเราเป็นระเบียบ ก็เพราะผู้คนจำนวนมากคิดถึงผู้อื่นด้วย ไม่ได้คิดถึงแต่ตัวเอง และสุดท้ายมันก็เป็นประโยชน์กับตัวเรา เพราะว่าพอสถานที่มันสะอาดหมดจด มันก็สบายหูสบายตา น่าอยู่
แต่ว่านิทานเรื่องนี้เขาสอนมากกว่านั้น ในการดำเนินชีวิตประจำวัน เราควรจะคิดถึงผู้อื่น มองไปที่ประโยชน์ของคนอื่นก่อนตัวเอง แต่เวลามีปัญหาขึ้นมา ก่อนที่จะไปโทษคนอื่น ต้องกลับมามองที่ตัวเองก่อน ไม่เหมือนกันนะ ยามปกติเรามองไปที่คนอื่นก่อน นึกถึงประโยชน์ของคนอื่นก่อน ประโยชน์ของตัวเองเอาไว้ทีหลัง แต่ว่าเวลามีปัญหา เราควรมองที่ตัวเองก่อนที่จะไปโทษคนอื่น
อย่างชายตาบอดนี่ พอมีคนมาชน แกก็ว่าชายคนนั้นเลยทีเดียว ว่าตาบอดหรือไง มาชนเขา แต่เขาไม่รู้ว่าที่เขาถูกชน เป็นเพราะว่าโคมของเขามันดับไปแล้ว ชายคนนั้นก็เลยมองไม่เห็น แต่ชายตาบอดจะรู้ได้อย่างไร ว่าโคมของตัวเองนี่ดับไปแล้ว อันนี้เหมือนกับสอนเป็นนัยว่าคนที่โทษคนอื่น แทนที่จะมองมาที่ตัวเอง จะว่าไปก็เหมือนกับคนตาบอด คือมองไม่เห็นความบกพร่อง ความผิดพลาดของตัวเอง อันนี้ก็รวมถึงคนตาดีด้วยนะ คนตาดีถ้าเกิดปัญหาขึ้นมาแล้ว ไปโทษคนอื่น แต่มองไม่เห็นความบกพร่อง ความผิดพลาดของตัวเอง ก็ไม่ต่างจากคนตาบอดเหมือนกัน
อันนี้ก็เป็นข้อคิดที่ดีมากเลย ในยามปกติเราควรนึกถึงผู้อื่น มองไปที่คนอื่นก่อน แต่เวลามีปัญหาควรจะกลับมามองที่ตัวเอง ก่อนที่จะไปโทษคนอื่น อันนี้จะเรียกว่าเป็นวิสัยของนักปฏิบัติธรรมก็ได้ จะเรียกว่าเป็นวิสัยของผู้ใฝ่ธรรม ซึ่งต่างจากวิสัยของชาวโลกทั่วๆ ไป ชาวโลกทั่วไปเขามองตัวเองก่อน เขามองถึงประโยชน์ตัวเองก่อน คิดถึงตัวเองก่อน ส่วนคนอื่น ประโยชน์ของคนอื่นเอาไว้ทีหลัง แต่เวลามีปัญหาขึ้นมา ก็โทษคนอื่นก่อนเลย แทนที่จะกลับมามองที่ตัวเอง
บ่อยครั้งเวลางานมีปัญหา เราจะเห็นคนก็จะไปโทษคนโน้นคนนี้ ว่าเป็นเหตุทำให้งานมีปัญหา ทำให้งานตัวเองมีปัญหา เจ้านายไม่ดี เพื่อนร่วมงานไม่ได้เรื่อง บางทีก็โทษดินฟ้าอากาศ แต่ว่าสิ่งที่ไม่ได้มองคือความผิดพลาดของตัวเอง เวลานัดเพื่อน เพื่อนไม่มาตามนัดตามเวลา ก็โกรธเพื่อน พอเจอเพื่อนก็ไปด่าเพื่อนเลย ว่าทำไมนัด 4 โมงเย็น ทำไมไม่มา อุตส่าห์รอ
เพื่อนบอกอ้าวจะไปรู้เหรอ นึกว่านัด 4 โมงเช้า ผมก็อุตส่าห์ไปรอตั้งแต่ 4 โมงเช้า คือ 10 โมง ปรากฏว่าคนนัดบอกเวลาไม่ละเอียด แทนที่จะบอก 4 โมงเย็น ก็ไปพูดว่า 4 โมง เพื่อนก็เลยนึกว่า 4 โมงเช้า เป็นความผิดพลาดของคนนัดแท้ๆ แต่ว่าก็ไปด่าเพื่อนเสียแล้ว ตัวเองพูดไม่ละเอียด ก็ไปโทษเพื่อน ว่าเพื่อนไม่รับผิดชอบ เพื่อนไม่เอาใจใส่
อันนี้เรียกว่าไปโทษคนอื่นก่อนที่จะมามองที่ตัวเอง ถ้าจะให้ดีก็ควรจะถามเขาก่อนว่าทำไมถึงไม่มาตามนัด พอรู้คำอธิบายของเพื่อน ก็อาจจะพบว่าเป็นเพราะเราผิดเองนะ เราพูดไม่รัดกุมเพียงพอ ที่จริงมันไม่ใช่เฉพาะเวลามีความผิดพลาด หรือเวลามีปัญหาในงานการ เวลามีความทุกข์ก็เหมือนกัน เวลามีความทุกข์ก่อนที่จะไปโทษใคร ต้องกลับมามองที่ตัวเองก่อน แต่คนส่วนใหญ่เวลามีความทุกข์ ไปโทษข้างนอก ไปโทษเสียงดังจากข้างนอก ไปโทษการกระทำของคนนั้นคนนี้ แต่ลืมหรือไม่ได้กลับมามองที่ตัวเอง ว่าเป็นที่เราหรือเปล่า
เวลามีความทุกข์ใจ สาเหตุหลักๆ มันล้วนแล้วแต่อยู่ที่ตัวเองทั้งนั้นแหละ ไม่ได้อยู่ที่คนอื่น ทุกข์กายอาจจะเป็นเพราะของแหลมมาแทง อาจจะเป็นเพราะเชื้อโรค เพราะอาหารเป็นพิษ หรือเพราะมีคนมาทำร้าย แต่ถ้าทุกข์ใจแล้วนี่ มันน่าจะเกิดจากตัวเอง หรือใจของตัวเองเป็นหลักเลยทีเดียว
เมื่อสัก 40 กว่าปีก่อน หลวงพ่อชาท่านได้รับนิมนต์ให้มาแสดงธรรมที่ประเทศอังกฤษ ตอนนั้นท่านก็มากับลูกศิษย์ที่เป็นพระฝรั่ง เช่นหลวงพ่อสุเมโธ ซึ่งตอนนั้นยังไม่ได้สร้างวัดอมราวดีที่อังกฤษ เจ้าภาพก็ให้หลวงพ่อชากับลูกศิษย์พักที่วิหารกลางกรุงลอนดอน ย่านนั้นมีสถานบันเทิง เช่น ผับ บาร์ กลางคืนก็จะมีเสียงดนตรี
สมัยนั้นดิสโก้ก็เริ่มเป็นที่นิยมแล้ว เพราะฉะนั้นเสียงดังก็จะกระหึ่มเลยตอนกลางคืน มาถึงวิหารแฮมสเตทที่หลวงพ่อชาและลูกศิษย์พัก ซึ่งก็พอดีเป็นช่วงที่ท่านพาคนนั่งสมาธิ พระและโยมหลายคนนั่งสมาธิไม่เป็นสุขเลย เพราะเสียงดนตรีมันดัง
แต่หลวงพ่อชาท่านนั่งสมาธิอย่างสงบ เหมือนกับไม่ได้ยินอะไรเลย จนกระทั่งนั่งสมาธิเสร็จ ก็มีโยมซึ่งเป็นฝรั่ง เป็นเจ้าภาพ ก็มาหาท่านแล้วก็บอกขอโทษ ที่เสียดนตรีรบกวนการนั่งสมาธิ หลวงพ่อชาท่านฟังแล้วก็ยิ้ม แล้วท่านก็พูดว่าโยมอย่าไปคิดว่าเสียงดนตรีรบกวนเรา ที่จริงเราต่างหากที่ไปรบกวนเสียงดนตรี
บางคนฟังแล้วก็งงนะ แต่ที่จริงที่ท่านพูดนี่มันเป็นสัจธรรมเลยนะ ที่คนมีความทุกข์ หงุดหงิด เมื่อเสียงมากระทบหู มันไม่ใช่เพราะเสียง แต่เป็นเพราะใจมันไปทะเลาะกับเสียงนั้น ใจมันไปต่อสู้ ไปทะเลาะเบาะแว้งกับเสียงนั้น มันไปผลักไสเสียงนั้น ถ้าเพียงแต่ยอมรับเสียงนั้น มันก็ไม่หงุดหงิด แต่พอใจมันทะเลาะกับเสียง เพราะว่ามีความรู้สึกเป็นลบต่อเสียงนั้น ว่าเป็นเสียงดัง เสียงรบกวน พอใจรู้สึกเป็นลบ มันหงุดหงิดขึ้นมาเลย ความหงุดหงิดจนนั่งสมาธิไม่เป็นสุข เป็นเพราะใจของคนฟัง ที่วางใจไม่ถูกต้องต่อเสียง ถ้าหากว่าเพียงแต่รู้สึกเป็นกลางๆ มันก็ไม่ทุกข์
มีนักปฏิบัติธรรมคนหนึ่ง แกก็มาปฏิบัติอยู่ที่สำนักหรือวัดแห่งหนึ่ง ก็ค้างคืนอยู่ประมาณ 2-3 คืน คืนแรกเลย พักเสร็จตื่นเช้าขึ้นมา เจ้าอาวาสก็ถามว่า เป็นยังไง หลับดีไหม ชายคนนั้นก็บอกว่าหลับไม่ค่อยดี โดยเฉพาะช่วงแรกๆ เพราะว่าเสียงห่านมันดัง
เสียงห่านมันดัง ตอนกลางคืนนอนไม่ค่อยหลับเลยช่วงแรก แต่ว่านึกขึ้นมาได้ว่าตัวเองพกโทรศัพท์มือถือมา แล้วในโทรศัพท์มือถือก็มีการอัดเทปคำบรรยายธรรมะของครูบาอาจารย์หลายท่าน ก็เลยเอาหูฟังใส่ไว้ในหู แล้วก็ฟัง เปิดเทปธรรมะ เปิดคำบรรยายของครูบาอาจารย์ จนกระทั่งหลับได้ กระทั่งเช้าก็เป็นอันว่าได้พัก ได้หลับดีหน่อยช่วงครึ่งหลัง
สิ่งที่น่าสนใจคือว่า ระหว่างเสียงห่านกับเสียงบรรยาย อะไรดังกว่ากัน ชายคนนั้นบอกว่าหลับไม่ได้ เพราะว่าเสียงห่านมันดัง แต่เสียงบรรยายที่ฟังมันไม่ดังหรือ ที่จริงมันดังกว่าเสียงห่าน เพราะว่าเอาหูฟังใส่เข้าไปในรูหู อย่างไรมันดังกว่าเสียงห่านอยู่แล้วล่ะ แต่ทำไมหลับ ก็เพราะใจมันยอมรับเสียงบรรยายธรรมะ หรือว่ารู้สึกดีกับเสียงนั้น ขณะที่เสียงห่านนี่ ใจมองว่าเป็นเสียงรบกวน การที่ใจไปตีค่าว่าเสียงห่านเป็นเสียงรบกวน ก็ทำให้เกิดอาการต่อสู้ผลักไสกับเสียงนั้น
เหมือนอย่างที่หลวงพ่อชาท่านว่าไปทะเลาะกับเสียง ส่วนเสียงบรรยายธรรมะที่ฟังทางโทรศัพท์มือถือ ใจมันยอมรับ ใจมันรู้สึกเป็นบวก เลยไม่รู้สึกว่าดัง ทั้งที่ถ้าพูดถึงเดซิเบลแล้ว มันดังกว่าเสียงห่านอยู่แล้วแต่ก็เป็นอันหลับได้ ฉะนั้นที่หลับไม่ได้ ไม่ใช่เพราะเสียงดัง ไม่ใช่เพราะเสียงห่าน แต่เพราะใจมันไปทะเลาะกับเสียงห่าน ในขณะที่เสียงบรรยายใจไม่ได้ทะเลาะ ใจไปเคลิ้มคล้อยกับเสียงบรรยายธรรมเลยหลับ
นี่เป็นตัวอย่างง่ายๆ ในชีวิตของคนเรา เวลามีความทุกข์ ทุกข์ใจ เรามักโทษข้างนอก โทษเสียงดนตรี โทษเสียงห่าน โทษคนนั้นคนนี้ แต่นั่นเป็นเพราะเราไม่ได้กลับมาดูใจของเรา ไม่ได้กลับมาสังเกตปฎิกริยาของใจเรา ฉะนั้นถ้าเรากลับมาสังเกต ก็จะพบว่ามันเป็นเพราะใจของเราต่างหาก ที่เป็นตัวการทำให้เกิดทุกข์
ฉะนั้นถ้าเกิดว่าเรามีทุกข์ หรือมีปัญหาขึ้นมาในใจ แล้วเราไปมองออกนอกตัว ไม่กลับมามองที่ตัว ก็ไม่ต่างจากชายตาบอด ที่ไปต่อว่าคนที่มาชนตัวเอง ทั้งที่โคมที่ตัวเองถือ ไฟมันดับไปนานแล้ว แต่มองไม่เห็น วิถีธรรมกับวิถีโลกมันต่างกัน วิถีโลก มีปัญหาอะไรก็โทษคนอื่น แต่เวลาสบายก็คิดถึงแต่ตัวเอง ส่วนวิถีธรรม เวลาสบายๆ เวลาปกติก็นึกถึงคนอื่น แต่เวลามีปัญหาก็กลับมองที่ตัวเองก่อน
แล้วที่จริงถ้าเราดู มันสะท้อนให้เห็นว่า วิถีโลกเขาเน้นในเรื่องการเปลี่ยนแปลง จัดการกับภายนอก แต่ว่าวิถีธรรมหรือวิถีของผู้ใฝ่ธรรม จะเน้นที่การเปลี่ยนแปลงที่ตัวเอง โดยเฉพาะการปรับเปลี่ยนใจของตัว เวลามีความทุกข์ก็ลองปรับเปลี่ยนใจ

เหมือนมีผู้ชายคนหนึ่งที่เขานั่งสมาธิทุกเช้าเป็นประจำ แล้วเขาก็นั่งได้ดีด้วย แต่วันหนึ่งปรากฏว่าพอนั่งไปได้สักครู่หนึ่ง ก็มีเสียงค้อนดัง ทีแรกก็เสียงค้อน ตอนหลังก็เสียงเลื่อยยนต์ เพราะมีการก่อสร้างใกล้ๆ ตอนที่เสียงค้อน เสียงเลื่อยยนต์มากระทบหู ใจนี่ก็กระเพื่อมเลย แต่เขามีสติเห็น สติรู้ทัน พอมีสติรู้ทัน ใจก็สงบ แต่พอเผลอ ใจก็กระเพื่อม ทุกครั้งที่เสียงเลื่อยยนต์ดังกระทบหู แล้วมันก็สงบลงพอมีสติรู้ทัน เป็นอย่างนี้พักหนึ่ง
เขาก็เลยลองไปพิจารณาที่เสียงเลื่อยยนต์ พอพิจารณาไปก็สังเกตว่าบางครั้งมันก็กระชากกระชั้น บางครั้งมันก็ลากยาว บางครั้งเสียงสูง บางครั้งเสียงต่ำ บางครั้งเสียงดัง บางครั้งเสียงเบา ดูๆไปแล้วมันเหมือนกับเสียงเพลงเลยนะ เพลงประเภท heavy metal พอทันทีที่มองว่ามันเป็นเสียงเพลง ใจก็สงบเลย สงบประเภทที่ว่าเพลินเลย
ที่จริงเพลินก็ไม่ดี แต่เขาก็อดฉุกคิดไม่ได้ เอ๊ะ เมื่อกี้ใจยังกระเพื่อมขึ้นกระเพื่อมลง แถมมีความหงุดหงิดด้วย ตอนนี้ทำไมใจมันสงบ มีบางช่วงเสียงเลื่อยยนต์มันหายไป เขาอยากให้เสียงมันดังกลับมาใหม่ เขาก็เลยแปลกใจ ทีแรกเราอยากให้เสียงมันดับไปหายไป แต่ทำไมตอนนี้อยากให้เสียงมันดังใหม่ เสียงมันก็ยังดังเหมือนเดิม แต่ทำไมความรู้สึกเปลี่ยนไป
ที่ความรู้สึกเปลี่ยนไปเพราะอะไร เพราะว่าไม่ได้มองว่ามันเป็นเสียงดังอีกต่อไป แต่มองว่ามันเป็นเสียงเพลง พอมองว่าเป็นเสียงเพลง ความรู้สึกมันเป็นความรู้สึกในทางบวก ใจก็สงบเลย อันนี้มันก็ชี้ให้เห็นว่าความสงบมันอยู่ที่ใจ มากกว่าอยู่ที่สิ่งภายนอก และที่หงุดหงิด ที่ไม่สงบ มันไม่ใช่เพราะสิ่งภายนอก แต่เป็นเพราะใจ ใจรู้สึกลบกับเสียง มันก็กระเพื่อม มันก็หงุดหงิด ไม่สงบ ไม่เป็นสุข แต่พอใจรู้สึกเป็นบวก ความรู้สึกก็เปลี่ยนเป็นตรงกันข้าม
ฉะนั้นแทนที่จะไปตะโกนโวกเวกว่าให้หยุดส่งเสียง ให้เลิกตอกตะปู ให้เลิกใช้เลื่อยยนต์ มันจะดีกว่าหรือเปล่า ถ้ากลับมาดูที่ใจของเรา กลับมาสังเกตที่ใจของเรา หรือกลับมาปรับใจของเรา ใจของเรานี่อาจจะเป็นปัญหา
อันนี้คล้ายๆ กับเมื่อ 2-3 วันก่อน มีพระรูปหนึ่งเล่าให้ฟัง ได้ยินเสียงตอนเช้าๆ ที่วัด ตอนสายๆ วันกรรมกร มันมีเสียงเครื่องยนต์ดัง ตอนนั้นก็คิดว่าเป็นเสียงมอเตอร์ไซค์ ทันทีที่คิดว่าเป็นเสียงมอเตอร์ไซค์ ไม่พอใจขึ้นมาทันทีเลย มันมาขี่มอเตอร์ไซค์อะไรกันตรงนี้ ในวัด
แต่สักประเดี๋ยวเดียวฉุกขึ้นมาว่าเอ๊ะ มันอาจจะไม่ใช่เสียงมอเตอร์ไซค์ก็ได้ อาจจะเป็นเสียงเลื่อย เลื่อยที่เขากำลังตัดไม้ที่โค่น เพราะว่าก่อนหน้านั้นมีไม้โค่น ทันทีที่นึกว่าเป็นเสียงเลื่อย ที่ใช้ตัดไม้ที่ล้มลง ใจมันสงบเลย กลับอนุโมทนาด้วย เขามาช่วยกันทำงาน เสียงก็เสียงเดิม แต่ทำไมทีแรกหงุดหงิด เพราะไปคิดว่าเสียงมอเตอร์ไซค์ และคิดต่อไปว่ามันมาขี่อะไรแถวนี้ ในวัด แต่พอมองว่าเป็นเสียงเลื่อยที่ใช้เลื่อยไม้ที่ล้ม ความรู้สึกมันเปลี่ยนไป เพราะเกิดความรู้สึกว่าเขากำลังทำหน้าที่ของเขา
ฉะนั้นสุขหรือทุกข์อยู่ที่ใจแท้ๆ เลย หงุดหงิดหรือว่าสงบ อยู่ที่ใจ ไม่ใช่อยู่ที่เสียง อยู่ที่ว่าเราจะมองมันอย่างไร ฉะนั้นถ้าเราเข้าใจตรงนี้ สังเกตใจของเรา เราจะพบว่าจะไปแก้ทุกข์ก็ต้องแก้ที่ใจนั่นแหละ ไม่ต้องไปแก้ที่คนอื่น เป็นเพราะใจเราวางไว้ผิด มันจึงทุกข์ มันจึงเกิดความหงุดหงิด เกิดความรำคาญ แต่พอเราปรับใจ เปลี่ยนมุมมอง ความรู้สึกก็เปลี่ยนไป
zen sukato บันทึกเสียง Nun & oi ถอดเสียง nok edit
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-23 19:32:28
@ 5d4b6c8d:8a1c1ee3
2025-05-23 19:32:28https://primal.net/e/nevent1qvzqqqqqqypzp6dtxy5uz5yu5vzxdtcv7du9qm9574u5kqcqha58efshkkwz6zmdqqszj207pl0eqkgld9vxknxamged64ch2x2zwhszupkut5v46vafuhg9833px
Some of my colleagues were talking about how they're even more scared of RFK Jr. than they are of Trump. I hope he earns it.
https://stacker.news/items/987685
-
 @ e3ba5e1a:5e433365
2025-02-05 17:47:16
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a friendly discussion on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
- Unlike full single payer, individuals incur high costs
- Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
- Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
- Reduce regulations significantly.
-
In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
- Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
- Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-
 @ 5144fe88:9587d5af
2025-05-23 17:01:37
@ 5144fe88:9587d5af
2025-05-23 17:01:37The recent anomalies in the financial market and the frequent occurrence of world trade wars and hot wars have caused the world's political and economic landscape to fluctuate violently. It always feels like the financial crisis is getting closer and closer.
This is a systematic analysis of the possibility of the current global financial crisis by Manus based on Ray Dalio's latest views, US and Japanese economic and financial data, Buffett's investment behavior, and historical financial crises.
Research shows that the current financial system has many preconditions for a crisis, especially debt levels, market valuations, and investor behavior, which show obvious crisis signals. The probability of a financial crisis in the short term (within 6-12 months) is 30%-40%,
in the medium term (within 1-2 years) is 50%-60%,
in the long term (within 2-3 years) is 60%-70%.
Japan's role as the world's largest holder of overseas assets and the largest creditor of the United States is particularly critical. The sharp appreciation of the yen may be a signal of the return of global safe-haven funds, which will become an important precursor to the outbreak of a financial crisis.
Potential conditions for triggering a financial crisis Conditions that have been met 1. High debt levels: The debt-to-GDP ratio of the United States and Japan has reached a record high. 2. Market overvaluation: The ratio of stock market to GDP hits a record high 3. Abnormal investor behavior: Buffett's cash holdings hit a record high, with net selling for 10 consecutive quarters 4. Monetary policy shift: Japan ends negative interest rates, and the Fed ends the rate hike cycle 5. Market concentration is too high: a few technology stocks dominate market performance
Potential trigger points 1. The Bank of Japan further tightens monetary policy, leading to a sharp appreciation of the yen and the return of overseas funds 2. The US debt crisis worsens, and the proportion of interest expenses continues to rise to unsustainable levels 3. The bursting of the technology bubble leads to a collapse in market confidence 4. The trade war further escalates, disrupting global supply chains and economic growth 5. Japan, as the largest creditor of the United States, reduces its holdings of US debt, causing US debt yields to soar
Analysis of the similarities and differences between the current economic environment and the historical financial crisis Debt level comparison Current debt situation • US government debt to GDP ratio: 124.0% (December 2024) • Japanese government debt to GDP ratio: 216.2% (December 2024), historical high 225.8% (March 2021) • US total debt: 36.21 trillion US dollars (May 2025) • Japanese debt/GDP ratio: more than 250%-263% (Japanese Prime Minister’s statement)
Before the 2008 financial crisis • US government debt to GDP ratio: about 64% (2007) • Japanese government debt to GDP ratio: about 175% (2007)
Before the Internet bubble in 2000 • US government debt to GDP ratio: about 55% (1999) • Japanese government debt to GDP ratio: about 130% (1999)
Key differences • The current US debt-to-GDP ratio is nearly twice that before the 2008 crisis • The current Japanese debt-to-GDP ratio is more than 1.2 times that before the 2008 crisis • Global debt levels are generally higher than historical pre-crisis levels • US interest payments are expected to devour 30% of fiscal revenue (Moody's warning)
Monetary policy and interest rate environment
Current situation • US 10-year Treasury yield: about 4.6% (May 2025) • Bank of Japan policy: end negative interest rates and start a rate hike cycle • Bank of Japan's holdings of government bonds: 52%, plans to reduce purchases to 3 trillion yen per month by January-March 2026 • Fed policy: end the rate hike cycle and prepare to cut interest rates
Before the 2008 financial crisis • US 10-year Treasury yield: about 4.5%-5% (2007) • Fed policy: continuous rate hikes from 2004 to 2006, and rate cuts began in 2007 • Bank of Japan policy: maintain ultra-low interest rates
Key differences • Current US interest rates are similar to those before the 2008 crisis, but debt levels are much higher than then • Japan is in the early stages of ending its loose monetary policy, unlike before historical crises • The size of global central bank balance sheets is far greater than at any time in history
Market valuations and investor behavior Current situation • The ratio of stock market value to the size of the US economy: a record high • Buffett's cash holdings: $347 billion (28% of assets), a record high • Market concentration: US stock growth mainly relies on a few technology giants • Investor sentiment: Technology stocks are enthusiastic, but institutional investors are beginning to be cautious
Before the 2008 financial crisis • Buffett's cash holdings: 25% of assets (2005) • Market concentration: Financial and real estate-related stocks performed strongly • Investor sentiment: The real estate market was overheated and subprime products were widely popular
Before the 2000 Internet bubble • Buffett's cash holdings: increased from 1% to 13% (1998) • Market concentration: Internet stocks were extremely highly valued • Investor sentiment: Tech stocks are in a frenzy
Key differences • Buffett's current cash holdings exceed any pre-crisis level in history • Market valuation indicators have reached a record high, exceeding the levels before the 2000 bubble and the 2008 crisis • The current market concentration is higher than any period in history, and a few technology stocks dominate market performance
Safe-haven fund flows and international relations Current situation • The status of the yen: As a safe-haven currency, the appreciation of the yen may indicate a rise in global risk aversion • Trade relations: The United States has imposed tariffs on Japan, which is expected to reduce Japan's GDP growth by 0.3 percentage points in fiscal 2025 • International debt: Japan is one of the largest creditors of the United States
Before historical crises • Before the 2008 crisis: International capital flows to US real estate and financial products • Before the 2000 bubble: International capital flows to US technology stocks
Key differences • Current trade frictions have intensified and the trend of globalization has weakened • Japan's role as the world's largest holder of overseas assets has become more prominent • International debt dependence is higher than any period in history
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:22
@ 04c915da:3dfbecc9
2025-05-20 15:50:22There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 26769dac:498e333b
2025-05-25 12:51:09
@ 26769dac:498e333b
2025-05-25 12:51:09Here's to the ones who can\ Feel there cause\ Surrender\ Change their ways\ But keep their fire\ And never give up
We will transform this world\ Restructuring\ One belief at a time
-
 @ 0fa80bd3:ea7325de
2025-01-29 05:55:02
@ 0fa80bd3:ea7325de
2025-01-29 05:55:02The land that belongs to the indigenous peoples of Russia has been seized by a gang of killers who have unleashed a war of extermination. They wipe out anyone who refuses to conform to their rules. Those who disagree and stay behind are tortured and killed in prisons and labor camps. Those who flee lose their homeland, dissolve into foreign cultures, and fade away. And those who stand up to protect their people are attacked by the misled and deceived. The deceived die for the unchecked greed of a single dictator—thousands from both sides, people who just wanted to live, raise their kids, and build a future.
Now, they are forced to make an impossible choice: abandon their homeland or die. Some perish on the battlefield, others lose themselves in exile, stripped of their identity, scattered in a world that isn’t theirs.
There’s been endless debate about how to fix this, how to clear the field of the weeds that choke out every new sprout, every attempt at change. But the real problem? We can’t play by their rules. We can’t speak their language or use their weapons. We stand for humanity, and no matter how righteous our cause, we will not multiply suffering. Victory doesn’t come from matching the enemy—it comes from staying ahead, from using tools they haven’t mastered yet. That’s how wars are won.
Our only resource is the will of the people to rewrite the order of things. Historian Timothy Snyder once said that a nation cannot exist without a city. A city is where the most active part of a nation thrives. But the cities are occupied. The streets are watched. Gatherings are impossible. They control the money. They control the mail. They control the media. And any dissent is crushed before it can take root.
So I started asking myself: How do we stop this fragmentation? How do we create a space where people can rebuild their connections when they’re ready? How do we build a self-sustaining network, where everyone contributes and benefits proportionally, while keeping their freedom to leave intact? And more importantly—how do we make it spread, even in occupied territory?
In 2009, something historic happened: the internet got its own money. Thanks to Satoshi Nakamoto, the world took a massive leap forward. Bitcoin and decentralized ledgers shattered the idea that money must be controlled by the state. Now, to move or store value, all you need is an address and a key. A tiny string of text, easy to carry, impossible to seize.
That was the year money broke free. The state lost its grip. Its biggest weapon—physical currency—became irrelevant. Money became purely digital.
The internet was already a sanctuary for information, a place where people could connect and organize. But with Bitcoin, it evolved. Now, value itself could flow freely, beyond the reach of authorities.
Think about it: when seedlings are grown in controlled environments before being planted outside, they get stronger, survive longer, and bear fruit faster. That’s how we handle crops in harsh climates—nurture them until they’re ready for the wild.
Now, picture the internet as that controlled environment for ideas. Bitcoin? It’s the fertile soil that lets them grow. A testing ground for new models of interaction, where concepts can take root before they move into the real world. If nation-states are a battlefield, locked in a brutal war for territory, the internet is boundless. It can absorb any number of ideas, any number of people, and it doesn’t run out of space.
But for this ecosystem to thrive, people need safe ways to communicate, to share ideas, to build something real—without surveillance, without censorship, without the constant fear of being erased.
This is where Nostr comes in.
Nostr—"Notes and Other Stuff Transmitted by Relays"—is more than just a messaging protocol. It’s a new kind of city. One that no dictator can seize, no corporation can own, no government can shut down.
It’s built on decentralization, encryption, and individual control. Messages don’t pass through central servers—they are relayed through independent nodes, and users choose which ones to trust. There’s no master switch to shut it all down. Every person owns their identity, their data, their connections. And no one—no state, no tech giant, no algorithm—can silence them.
In a world where cities fall and governments fail, Nostr is a city that cannot be occupied. A place for ideas, for networks, for freedom. A city that grows stronger the more people build within it.
-
 @ 000002de:c05780a7
2025-05-22 20:50:21
@ 000002de:c05780a7
2025-05-22 20:50:21I'm mostly curious about how Tapper can do this with a straight face.
https://stacker.news/items/986926
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ 6be5cc06:5259daf0
2025-01-21 20:58:37
@ 6be5cc06:5259daf0
2025-01-21 20:58:37A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
-
 @ 4fe14ef2:f51992ec
2025-05-25 10:04:36
@ 4fe14ef2:f51992ec
2025-05-25 10:04:36Let's support Bitcoin merchants! I'd love to hear some of your latest Lightning purchases and interesting products you bought. Feel free to include links to the shops or businesses you bought from.
Who else has a recent purchase they’re excited about? Bonus sats if you found a killer deal! ⚡
Spend sats, not fiat!
If you missed our last thread, here are some of the items stackers recently spent and zap on.
Share and repost: N: https://njump.me/note1r0rllvtns2e8g2rqn0p9uytxucmjzal3pxslldjtfmxwp2amwjjqy3aazq X: https://x.com/AGORA_SN/status/1926579498629169410
https://stacker.news/items/988783
-
 @ 9e69e420:d12360c2
2025-01-21 19:31:48
@ 9e69e420:d12360c2
2025-01-21 19:31:48Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits.
Active Compounds
The oil's therapeutic properties stem from its key bioactive components: - Carvacrol and thymol (primary active compounds) - Polyphenols and other antioxidant
Antimicrobial Properties
Bacterial Protection The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance.
Antifungal Effects It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections.
Digestive Health Benefits
Oregano oil supports digestive wellness by: - Promoting gastric juice secretion and enzyme production - Helping treat Small Intestinal Bacterial Overgrowth (SIBO) - Managing digestive discomfort, bloating, and IBS symptoms
Anti-inflammatory and Antioxidant Effects
The oil provides significant protective benefits through: - Powerful antioxidant activity that fights free radicals - Reduction of inflammatory markers in the body - Protection against oxidative stress-related conditions
Respiratory Support
It aids respiratory health by: - Loosening mucus and phlegm - Suppressing coughs and throat irritation - Supporting overall respiratory tract function
Additional Benefits
Skin Health - Improves conditions like psoriasis, acne, and eczema - Supports wound healing through antibacterial action - Provides anti-aging benefits through antioxidant properties
Cardiovascular Health Studies show oregano oil may help: - Reduce LDL (bad) cholesterol levels - Support overall heart health
Pain Management The oil demonstrates effectiveness in: - Reducing inflammation-related pain - Managing muscle discomfort - Providing topical pain relief
Safety Note
While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications.
-
 @ d419d542:b8bfb32d
2025-05-25 10:02:26
@ d419d542:b8bfb32d
2025-05-25 10:02:26Sự bùng nổ của công nghệ số đã làm thay đổi cách người Việt tiếp cận và tận hưởng các loại hình giải trí, từ truyền hình, âm nhạc đến các nền tảng trực tuyến. Trong làn sóng chuyển đổi này, 42VN nổi bật như một trong những đơn vị tiên phong ứng dụng công nghệ hiện đại để mang đến trải nghiệm giải trí số hoàn toàn mới cho người dùng trong nước. Không chỉ cung cấp một nền tảng trực quan, dễ sử dụng, 42VN còn kết hợp giữa thiết kế thân thiện và khả năng cá nhân hóa nội dung dựa trên hành vi người dùng, từ đó tạo nên môi trường tương tác linh hoạt, phù hợp với mọi độ tuổi và phong cách sống. Việc tích hợp đa dạng dịch vụ giải trí số trên cùng một nền tảng không chỉ giúp người dùng tiết kiệm thời gian tìm kiếm mà còn nâng cao tính tiện lợi và khả năng truy cập mọi lúc, mọi nơi. Đây là một bước tiến đáng kể góp phần thúc đẩy xu hướng giải trí tại nhà – điều ngày càng phổ biến trong xã hội hiện đại, đặc biệt sau những thay đổi trong thói quen sinh hoạt hậu đại dịch.
Bên cạnh đó, 42VN còn đầu tư vào các yếu tố công nghệ nhằm nâng cao tốc độ truy cập, tối ưu khả năng xử lý dữ liệu và bảo mật thông tin cá nhân của người dùng. Hệ thống máy chủ hiện đại, khả năng tương thích đa thiết bị và giao diện hoàn toàn bằng tiếng Việt giúp mọi người dùng, kể cả người ít kinh nghiệm công nghệ, cũng dễ dàng tiếp cận và sử dụng. Quan trọng hơn, nền tảng này không chỉ đơn thuần là công cụ giải trí mà còn góp phần thúc đẩy tư duy sử dụng công nghệ một cách tích cực và có trách nhiệm. Việc 42VN thường xuyên cập nhật các tính năng mới, tổ chức các hoạt động tương tác và lắng nghe ý kiến người dùng cho thấy chiến lược phát triển lâu dài của họ không nằm ở việc cung cấp dịch vụ một chiều, mà là xây dựng một cộng đồng số năng động, thân thiện và bền vững. Trong tương lai, khi nhu cầu giải trí kỹ thuật số ngày càng gia tăng, mô hình hoạt động và định hướng đổi mới của 42VN chắc chắn sẽ đóng vai trò quan trọng trong việc hình thành một thế hệ người dùng Việt am hiểu công nghệ, yêu thích trải nghiệm số và sẵn sàng đón nhận những xu hướng mới của thời đại.
-
 @ cefb08d1:f419beff
2025-05-22 07:16:18
@ cefb08d1:f419beff
2025-05-22 07:16:18https://stacker.news/items/986402
-
 @ 26769dac:498e333b
2025-05-25 12:24:47
@ 26769dac:498e333b
2025-05-25 12:24:47Here's to the ones who can\ Feel there cause\ Surrender\ Change their ways\ But keep their fire\ And never give up
We will transform this world\ Restructuring\ One belief at a time
-
 @ 3283ef81:0a531a33
2025-05-25 12:14:51
@ 3283ef81:0a531a33
2025-05-25 12:14:51Aliquam eu turpis sed enim ultricies scelerisque\ Duis posuere congue faucibus
Praesent pretium orci ante, et faucibus lectus euismod a
-
 @ 3f770d65:7a745b24
2025-05-19 18:09:52
@ 3f770d65:7a745b24
2025-05-19 18:09:52🏌️ Monday, May 26 – Bitcoin Golf Championship & Kickoff Party
Location: Las Vegas, Nevada\ Event: 2nd Annual Bitcoin Golf Championship & Kick Off Party"\ Where: Bali Hai Golf Clubhouse, 5160 S Las Vegas Blvd, Las Vegas, NV 89119\ 🎟️ Get Tickets!
Details:
-
The week tees off in style with the Bitcoin Golf Championship. Swing clubs by day and swing to music by night.
-
Live performances from Nostr-powered acts courtesy of Tunestr, including Ainsley Costello and others.
-
Stop by the Purple Pill Booth hosted by Derek and Tanja, who will be on-boarding golfers and attendees to the decentralized social future with Nostr.
💬 May 27–29 – Bitcoin 2025 Conference at the Las Vegas Convention Center
Location: The Venetian Resort\ Main Attraction for Nostr Fans: The Nostr Lounge\ When: All day, Tuesday through Thursday\ Where: Right outside the Open Source Stage\ 🎟️ Get Tickets!
Come chill at the Nostr Lounge, your home base for all things decentralized social. With seating for \~50, comfy couches, high-tops, and good vibes, it’s the perfect space to meet developers, community leaders, and curious newcomers building the future of censorship-resistant communication.
Bonus: Right across the aisle, you’ll find Shopstr, a decentralized marketplace app built on Nostr. Stop by their booth to explore how peer-to-peer commerce works in a truly open ecosystem.
Daily Highlights at the Lounge:
-
☕️ Hang out casually or sit down for a deeper conversation about the Nostr protocol
-
🔧 1:1 demos from app teams
-
🛍️ Merch available onsite
-
🧠 Impromptu lightning talks
-
🎤 Scheduled Meetups (details below)
🎯 Nostr Lounge Meetups
Wednesday, May 28 @ 1:00 PM
- Damus Meetup: Come meet the team behind Damus, the OG Nostr app for iOS that helped kickstart the social revolution. They'll also be showcasing their new cross-platform app, Notedeck, designed for a more unified Nostr experience across devices. Grab some merch, get a demo, and connect directly with the developers.
Thursday, May 29 @ 1:00 PM
- Primal Meetup: Dive into Primal, the slickest Nostr experience available on web, Android, and iOS. With a built-in wallet, zapping your favorite creators and friends has never been easier. The team will be on-site for hands-on demos, Q\&A, merch giveaways, and deeper discussions on building the social layer of Bitcoin.
🎙️ Nostr Talks at Bitcoin 2025
If you want to hear from the minds building decentralized social, make sure you attend these two official conference sessions:
1. FROSTR Workshop: Multisig Nostr Signing
-
🕚 Time: 11:30 AM – 12:00 PM
-
📅 Date: Wednesday, May 28
-
📍 Location: Developer Zone
-
🎤 Speaker: nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgdwaehxw309ahx7uewd3hkcqpqs9etjgzjglwlaxdhsveq0qksxyh6xpdpn8ajh69ruetrug957r3qf4ggfm (Austin Kelsay) @ Voltage\ A deep-dive into FROST-based multisig key management for Nostr. Geared toward devs and power users interested in key security.
2. Panel: Decentralizing Social Media
-
🕑 Time: 2:00 PM – 2:30 PM
-
📅 Date: Thursday, May 29
-
📍 Location: Genesis Stage
-
🎙️ Moderator: nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqy08wumn8ghj7mn0wd68yttjv4kxz7fwv3jhyettwfhhxuewd4jsqgxnqajr23msx5malhhcz8paa2t0r70gfjpyncsqx56ztyj2nyyvlq00heps - Bitcoin Strategy @ Roxom TV
-
👥 Speakers:
-
nostr:nprofile1qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcppemhxue69uhkummn9ekx7mp0qqsy2ga7trfetvd3j65m3jptqw9k39wtq2mg85xz2w542p5dhg06e5qmhlpep – Early Bitcoin dev, CEO @ Sirius Business Ltd
-
nostr:nprofile1qy2hwumn8ghj7mn0wd68ytndv9kxjm3wdahxcqg5waehxw309ahx7um5wfekzarkvyhxuet5qqsw4v882mfjhq9u63j08kzyhqzqxqc8tgf740p4nxnk9jdv02u37ncdhu7e3 – Analyst & Partner @ Ego Death Capital
Get the big-picture perspective on why decentralized social matters and how Nostr fits into the future of digital communication.
🌃 NOS VEGAS Meetup & Afterparty
Date: Wednesday, May 28\ Time: 7:00 PM – 1:00 AM\ Location: We All Scream Nightclub, 517 Fremont St., Las Vegas, NV 89101\ 🎟️ Get Tickets!
What to Expect:
-
🎶 Live Music Stage – Featuring Ainsley Costello, Sara Jade, Able James, Martin Groom, Bobby Shell, Jessie Lark, and other V4V artists
-
🪩 DJ Party Deck – With sets by nostr:nprofile1qy0hwumn8ghj7cmgdae82uewd45kketyd9kxwetj9e3k7mf6xs6rgqgcwaehxw309ahx7um5wgh85mm694ek2unk9ehhyecqyq7hpmq75krx2zsywntgtpz5yzwjyg2c7sreardcqmcp0m67xrnkwylzzk4 , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgkwaehxw309anx2etywvhxummnw3ezucnpdejqqg967faye3x6fxgnul77ej23l5aew8yj0x2e4a3tq2mkrgzrcvecfsk8xlu3 , and more DJs throwing down
-
🛰️ Live-streamed via Tunestr
-
🧠 Nostr Education – Talks by nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq37amnwvaz7tmwdaehgu3dwfjkccte9ejx2un9ddex7umn9ekk2tcqyqlhwrt96wnkf2w9edgr4cfruchvwkv26q6asdhz4qg08pm6w3djg3c8m4j , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqg7waehxw309anx2etywvhxummnw3ezucnpdejz7ur0wp6kcctjqqspywh6ulgc0w3k6mwum97m7jkvtxh0lcjr77p9jtlc7f0d27wlxpslwvhau , nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq3vamnwvaz7tmwdaehgu3wd33xgetk9en82m30qqsgqke57uygxl0m8elstq26c4mq2erz3dvdtgxwswwvhdh0xcs04sc4u9p7d , nostr:nprofile1q9z8wumn8ghj7erzx3jkvmmzw4eny6tvw368wdt8da4kxamrdvek76mrwg6rwdngw94k67t3v36k77tev3kx7vn2xa5kjem9dp4hjepwd3hkxctvqyg8wumn8ghj7mn0wd68ytnhd9hx2qpqyaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgssuy4zk , nostr:nprofile1qy28wue69uhnzvpwxqhrqt33xgmn5dfsx5cqz9thwden5te0v4jx2m3wdehhxarj9ekxzmnyqqswavgevxe9gs43vwylumr7h656mu9vxmw4j6qkafc3nefphzpph8ssvcgf8 , and more.
-
🧾 Vendors & Project Booths – Explore new tools and services
-
🔐 Onboarding Stations – Learn how to use Nostr hands-on
-
🐦 Nostrich Flocking – Meet your favorite nyms IRL
-
🍸 Three Full Bars – Two floors of socializing overlooking vibrant Fremont Street
| | | | | ----------- | -------------------- | ------------------- | | Time | Name | Topic | | 7:30-7:50 | Derek | Nostr for Beginners | | 8:00-8:20 | Mark & Paul | Primal | | 8:30-8:50 | Terry | Damus | | 9:00-9:20 | OpenMike and Ainsley | V4V | | 09:30-09:50 | The Space | Space |
This is the after-party of the year for those who love freedom technology and decentralized social community. Don’t miss it.
Final Thoughts
Whether you're there to learn, network, party, or build, Bitcoin 2025 in Las Vegas has a packed week of Nostr-friendly programming. Be sure to catch all the events, visit the Nostr Lounge, and experience the growing decentralized social revolution.
🟣 Find us. Flock with us. Purple pill someone.
-
-
 @ 866e0139:6a9334e5
2025-05-25 11:03:13
@ 866e0139:6a9334e5
2025-05-25 11:03:13Autor: Alexa Rodrian. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
„Triff niemals deine Idole“ heißt ein gängiger Ratschlag. In gewendeten Zeiten stehen zu dem die Werte auf dem Kopf – und manche Künstler mit ihnen. Die Worte, die aus manch ihrer Mündern kommen, wirken, als hätte eine fremde Hand sie auf deren Zunge gelegt.
Die Sängerin Alexa Rodrian erlebte bei der Verleihung des Deutschen Filmpreises einen solchen Moment der Desillusion. Es war der Auftritt des Liedermachers Wolf Biermann. Hören Sie hierzu Alexa Rodrians Text „Wolf Biermann und sein falscher Friede“.
https://soundcloud.com/radiomuenchen/wolf-biermann-und-sein-falscher-friede-von-alexa-rodrian
Dieser Beitrag erschien zuerst auf Radio München.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 6be5cc06:5259daf0
2025-01-21 01:51:46
@ 6be5cc06:5259daf0
2025-01-21 01:51:46Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas.
Satoshi Nakamoto
satoshin@gmx.com
www.bitcoin.org
Resumo
O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado gasto duplo, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações.
As transações são registradas em um livro público chamado blockchain, protegido por uma técnica chamada Prova de Trabalho. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira.
Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu.
1. Introdução
Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em confiança.
Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável.
Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável.
O que precisamos é de um sistema de pagamento eletrônico baseado em provas matemáticas, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas.
Neste documento, apresentamos o Bitcoin, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques.
2. Transações
Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital.
O que é uma assinatura digital?
Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso.
Como funciona na prática?
Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário:
- A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1.
- Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2.
- Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda.
Resolvendo o problema do gasto duplo
Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro.
O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain.
Por que isso é importante?
Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes.
3. Servidor Timestamp
Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica.
Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público.
Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain.
Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada.
O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin.
4. Prova-de-Trabalho
Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente.
A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita.
Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain.
A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos.
Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional.
5. Rede
A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são:
-
Transmissão de Transações: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la.
-
Coleta de Transações em Blocos: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain).
-
Prova-de-Trabalho: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil.
-
Envio do Bloco Resolvido: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede.
-
Validação do Bloco: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos.
-
Construção do Próximo Bloco: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia.
Resolução de Conflitos e Escolha da Cadeia Mais Longa
Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia.
Tolerância a Falhas
A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido.
Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central.
6. Incentivo
O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação.
Recompensa por Mineração
Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho.
Taxas de Transação
Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo.
Incentivo à Honestidade
O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas:
- Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos.
- Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas.
A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema.
Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo.
7. Recuperação do Espaço em Disco
Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações.
Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados.
Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados.
Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo.
8. Verificação de Pagamento Simplificada
É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada.
Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação.
A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede.
Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável.
9. Combinando e Dividindo Valor
No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor.
Entradas e Saídas
Cada transação no Bitcoin é composta por:
- Entradas: Representam os valores recebidos em transações anteriores.
- Saídas: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente.
Normalmente, uma transação contém:
- Uma única entrada com valor suficiente para cobrir o pagamento.
- Ou várias entradas combinadas para atingir o valor necessário.
O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como troco.
Exemplo Prático
Imagine que você tem duas entradas:
- 0,03 BTC
- 0,07 BTC
Se deseja enviar 0,08 BTC para alguém, a transação terá:
- Entrada: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC).
- Saídas: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC).
Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente.
Difusão e Simplificação
A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade.
10. Privacidade
O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando chaves públicas anônimas, que desvinculam diretamente as transações das identidades das partes envolvidas.
Fluxo de Informação
- No modelo tradicional, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário.
- No Bitcoin, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não.
Protegendo a Privacidade
Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas:
- Chaves Públicas Anônimas: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único.
- Prevenção de Ligação: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário.
Riscos de Ligação
Embora a privacidade seja fortalecida, alguns riscos permanecem:
- Transações multi-entrada podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total.
- O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas.
11. Cálculos
Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito.
Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira.
Mas isso é extremamente difícil.
Como o Ataque Funciona
Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido.
- Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira.
- O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida.
Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente.
A Corrida Entre Cadeias
Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos.
Suponha que:
- A rede honesta tem 80% do poder computacional (ou seja, resolve 8 de cada 10 quebra-cabeças).
- O atacante tem 20% do poder computacional (ou seja, resolve 2 de cada 10 quebra-cabeças).
Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar.
Por Que o Ataque Fica Cada Vez Mais Improvável?
Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos:
P = (q/p)^z
- q é o poder computacional do atacante (20%, ou 0,2).
- p é o poder computacional da rede honesta (80%, ou 0,8).
- z é a diferença de blocos entre a cadeia honesta e a cadeia do atacante.
Se o atacante está 5 blocos atrás (z = 5):
P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%)
Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável.
Se ele estiver 10 blocos atrás (z = 10):
P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%).
Neste caso, as chances de sucesso são praticamente nulas.
Um Exemplo Simples
Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível.
No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática.
Por Que Tudo Isso é Seguro?
- A probabilidade de sucesso do atacante diminui exponencialmente. Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema.
- A cadeia verdadeira (honesta) está protegida pela força da rede. Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar.
E Se o Atacante Tentar Continuar?
O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil.
Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso.
12. Conclusão
Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos.
Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
-
 @ b83a28b7:35919450
2025-05-16 19:26:56
@ b83a28b7:35919450
2025-05-16 19:26:56This article was originally part of the sermon of Plebchain Radio Episode 111 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ d419d542:b8bfb32d
2025-05-25 10:01:03
@ d419d542:b8bfb32d
2025-05-25 10:01:03Trong thế giới công nghệ số ngày càng phát triển, giao diện người dùng (UI) đóng vai trò ngày càng quan trọng trong việc thu hút và giữ chân người dùng. Với OK22, giao diện không đơn thuần chỉ là phương tiện kết nối giữa người và hệ thống, mà còn là yếu tố tạo nên trải nghiệm hoàn hảo. Từ cách bố trí các nút chức năng, màu sắc cho đến tốc độ phản hồi khi tương tác, tất cả đều được tối ưu hóa nhằm đảm bảo rằng người dùng cảm thấy thoải mái, dễ thao tác và tin tưởng vào nền tảng. OK22 chú trọng thiết kế giao diện dựa trên hành vi người dùng thực tế, nghĩa là họ không chỉ thiết kế theo thị hiếu mà còn nghiên cứu kỹ càng thói quen, tần suất và nhu cầu sử dụng của từng nhóm người dùng. Nhờ vậy, người dùng dù mới tiếp cận lần đầu cũng có thể nhanh chóng làm quen với hệ thống mà không cần thời gian học hỏi dài. Không những vậy, việc liên tục cập nhật các xu hướng thiết kế mới giúp OK22 luôn giữ được vẻ hiện đại và sự chuyên nghiệp, từ đó tạo nên ấn tượng tích cực trong mắt người dùng ngay từ lần đầu sử dụng.
OK22 không chỉ dừng lại ở giao diện người dùng trực quan mà còn kết hợp chặt chẽ với trải nghiệm người dùng (UX) nhằm mang lại cảm giác liền mạch, thống nhất và tiện lợi trong mọi thao tác. Bằng cách tạo ra luồng thao tác ngắn gọn, logic và dễ hiểu, nền tảng giúp người dùng tiết kiệm thời gian và công sức trong suốt quá trình sử dụng. Tính năng tìm kiếm thông minh, cá nhân hóa nội dung và hỗ trợ trực tuyến được tích hợp khéo léo vào giao diện, giúp người dùng luôn cảm thấy được hỗ trợ kịp thời và đúng nhu cầu. OK22 cũng rất quan tâm đến khía cạnh bảo mật và quyền riêng tư, vì vậy các thông báo, xác thực và lựa chọn quyền truy cập được bố trí rõ ràng, dễ quản lý. Việc đồng bộ hóa thiết kế trên các nền tảng khác nhau như web, ứng dụng di động và phiên bản nhẹ cũng giúp người dùng có được cảm nhận nhất quán dù sử dụng thiết bị nào. Tất cả những điều đó chứng minh rằng việc đầu tư vào giao diện và trải nghiệm người dùng không chỉ là xu hướng, mà còn là chiến lược lâu dài giúp OK22 duy trì lợi thế cạnh tranh, gia tăng sự hài lòng và khẳng định vị thế trong lĩnh vực công nghệ số hiện đại.
-
 @ f9cf4e94:96abc355
2025-01-18 06:09:50
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |
 | Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |
| Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |  | 16Gb |
| 16Gb |Recomendo que use o Ubuntu Server para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi aqui. O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível aqui. Não instale um desktop (como xubuntu, lubuntu, xfce, etc.).
Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
bash apt update apt install tor
Passo 2: Criar o Arquivo de Serviço
nrs.service🔧Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit [Unit] Description=Nostr Relay Server Service After=network.target
[Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure
[Install] WantedBy=multi-user.target ```
Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr aqui no GitHub.
Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
bash mkdir -p /opt/nrs /mnt/edriver
Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
bash lsblk
Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo,
/dev/sda) e formate-o:bash mkfs.vfat /dev/sda
Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta
/mnt/edriver:bash mount /dev/sda /mnt/edriver
Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
bash blkid
Passo 9: Alterar o
fstabpara Montar o Pendrive Automáticamente 📝Abra o arquivo
/etc/fstabe adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta
/opt/nrs:bash cp nrs-arm64 /opt/nrs
Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em
/opt/nrs/config.yaml:yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true
Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo
nrs.servicepara o diretório/etc/systemd/system/:bash cp nrs.service /etc/systemd/system/Recarregue os serviços e inicie o serviço
nrs:bash systemctl daemon-reload systemctl enable --now nrs.service
Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor
/var/lib/tor/torrce adicione a seguinte linha:torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334
Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
bash systemctl enable --now tor.serviceO Tor irá gerar um endereço
.onionpara o seu servidor Nostr. Você pode encontrá-lo no arquivo/var/lib/tor/nostr_server/hostname.
Observações ⚠️
- Com essa configuração, os dados serão salvos no pendrive, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço
.oniondo seu servidor Nostr será algo como:ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion.
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-
 @ c1d77557:bf04ec8b
2025-05-25 09:47:07
@ c1d77557:bf04ec8b
2025-05-25 09:47:07No crescente universo de plataformas de jogos online, a H2Bet se destaca como uma opção inovadora, segura e recheada de diversão para os jogadores brasileiros. Com uma interface moderna e intuitiva, a H2Bet vem conquistando cada vez mais usuários que buscam entretenimento de qualidade, diversas opções de jogos e uma experiência digital fluida e confiável.
Uma Plataforma Feita para o Público Brasileiro Desde o primeiro acesso, é possível perceber que a H2Bet foi pensada para atender às necessidades do público brasileiro. O site é totalmente traduzido para o português, com suporte ao cliente eficiente e disponível 24 horas por dia, todos os dias da semana. O atendimento pode ser feito via chat ao vivo ou WhatsApp, oferecendo respostas rápidas e eficazes para qualquer dúvida ou solicitação.
Além disso, a plataforma aceita métodos de pagamento populares no Brasil, como PIX, boleto bancário e carteiras digitais, garantindo mais praticidade nas transações financeiras. Isso facilita tanto os depósitos quanto os saques, promovendo uma experiência mais fluida para todos os jogadores.
Diversidade de Jogos para Todos os Gostos Um dos grandes diferenciais da H2Betestá em sua ampla variedade de jogos. A plataforma oferece opções para todos os perfis de jogadores — desde os iniciantes até os mais experientes. Entre os destaques estão:
Slots (Caça-níqueis): Com gráficos envolventes, animações modernas e uma enorme variedade de temas, os slots são perfeitos para quem busca diversão rápida e visualmente atrativa.
Jogos de Mesa: Clássicos como roleta, blackjack e bacará estão presentes na H2Bet, proporcionando uma experiência dinâmica e estratégica para os jogadores que gostam de desafios mentais.
Apostas Esportivas: Os fãs de esportes também têm espaço garantido na H2Bet. É possível apostar em jogos de futebol, basquete, tênis e diversas outras modalidades, tanto nacionais quanto internacionais.
A plataforma trabalha com provedores de jogos renomados mundialmente, garantindo alta qualidade gráfica, jogabilidade otimizada e total segurança nos resultados.
Uma Experiência do Jogador Incomparável Na H2Bet, a experiência do usuário é prioridade. Tudo foi cuidadosamente projetado para que o jogador possa se divertir sem complicações. O processo de cadastro é rápido e simplificado, permitindo que o novo usuário comece a jogar em poucos minutos. Além disso, o site é totalmente responsivo, funcionando perfeitamente em computadores, tablets e smartphones.
Outro ponto de destaque são as promoções e bônus oferecidos aos jogadores. Desde bônus de boas-vindas até promoções sazonais e programas de fidelidade, a H2Bet recompensa a lealdade dos seus usuários com benefícios exclusivos que aumentam ainda mais a diversão.
A segurança da plataforma também merece elogios. A H2Bet utiliza tecnologia de criptografia de ponta para proteger os dados dos jogadores, além de manter total transparência em seus termos e condições.
Conclusão A H2Bet chega ao mercado brasileiro com uma proposta clara: oferecer uma plataforma de jogos online completa, segura e envolvente. Com uma vasta seleção de jogos, suporte dedicado ao jogador e uma interface pensada para o usuário, a H2Bet se posiciona como uma das melhores opções de entretenimento digital no Brasil. Se você busca emoção, praticidade e uma experiência de jogo diferenciada, a H2Bet é o lugar certo para você.
-
 @ 975e4ad5:8d4847ce
2025-05-25 10:43:35
@ 975e4ad5:8d4847ce
2025-05-25 10:43:35Selfishness as Bitcoin’s Engine
Bitcoin, created by Satoshi Nakamoto, operates on a clear mechanism: miners use computational power to solve complex mathematical puzzles, verifying transactions on the network. In return, they earn rewards in Bitcoin. This is pure self-interest—miners want to maximize their profits. But while pursuing personal gain, they inadvertently maintain the entire system. Each new block added to the blockchain makes the network more stable and resilient against attacks. The more miners join, the more decentralized the system becomes, rendering it nearly impossible to manipulate.
This mechanism is brilliant because it taps into human nature—the desire for personal gain—to create something greater. Bitcoin doesn’t rely on altruism or good intentions. It relies on rational self-interest, which drives individuals to act in their own favor, ultimately benefiting the entire community.
The World Works the Same Way
This concept isn’t unique to Bitcoin. The world is full of examples where personal interest leads to collective progress. When an entrepreneur creates a new product, they do so to make money, but in the process, they create jobs, advance technology, and improve people’s lives. When a scientist works on a breakthrough, they may be driven by fame or financial reward, but the result is often a discovery that changes the world. Even in everyday life, when we buy products or services for our own convenience, we support the economy and encourage innovation.
Of course, self-interest doesn’t always lead to positive outcomes. Technologies created with good intentions can be misused—for example, in wars or for fraud. But even these negative aspects don’t halt progress. Competition and the drive for survival push humanity to find solutions, learn from mistakes, and keep moving forward. This is the cycle of development: individual self-interest fuels innovations that make the world more technological and connected.
Nature and Bitcoin: The DNA Parallel
To understand this mechanism, let’s look to nature. Consider the cells in a living organism. Each cell operates independently, following the instructions encoded in its DNA—a code that dictates its actions. The cell doesn’t “know” about the entire body, nor does it care. It simply strives for its own survival, performing its functions. But when billions of cells work together, following this code, they create something greater—a living organism.
Bitcoin is like the DNA of a decentralized system. Each miner is like a cell, following the “instructions” of the protocol to survive (profit). They don’t think about the entire network, only their own reward. But when all miners act together, they create something bigger—a global, secure, and resilient financial system. This is the beauty of decentralization: everyone acts for themselves, but the result is collective.
Selfishness and Humanity
Humans are no different from cells. Each of us wants to thrive—to have security, comfort, and success. But in pursuing these goals, we contribute to society. A teacher educates because they want to earn a living, but they shape future generations. An engineer builds a bridge because it’s their job, but it facilitates transportation for millions. Even in our personal lives, when we care for our families, we strengthen the social bonds that make society stronger.
Of course, there are exceptions—people who act solely for personal gain without regard for consequences. But even these outliers don’t change the bigger picture. Selfishness, when channeled correctly, is a driver of progress. Bitcoin is proof of this—a technology that turns personal interest into global innovation.
Bitcoin is more than just a cryptocurrency; it’s a mirror of human nature and the way the world works. Its design harnesses selfishness to create something sustainable and valuable. Just like cells in a body or people in society, Bitcoin miners work for themselves but contribute to something greater. It’s a reminder that even in our pursuit of personal gain, we can make the world a better place—as long as we follow the right “code.”
-
 @ 000002de:c05780a7
2025-05-21 20:00:21
@ 000002de:c05780a7
2025-05-21 20:00:21I enjoy Jonathan Pageau's perspectives from time to time. He is big on myth and symbolic signs in culture and history. I find this stuff fascinating as well. I watched this video last week, and based on the title, I was thinking... hmm, I wonder if it is a review of Return of the Strong Gods. It wasn't, but it really flows with the thesis of that book. You should read it if you haven't, and before you do, go check out @SimpleStacker's review of it.
Pageau starts the video by talking about the concept of "watching the clown." He uses Ye as the clown. Ye has been a leading indicator in the past when he publicly claimed he was a Christian and began making music and holding church services. Now he's going "off the rails" seemingly with his Hitler songs and art. Clearly, the stigma of Hitler will not last forever. It's hard for us to realize this. At least for someone of my age, but Pageau points out that eventually, the villains of history become less of a stand-in for Satan and more of a purely historical figure. He mentions Alexander the Great as a man who did incredibly evil things, but today we just read about him in school and don't really think about it too much. One day, that will be the way Hitler is viewed. Sure, evil, but the power of using him as the mythical Satan will wane.
The most interesting point I took away from this video, though, was that the post-war consensus was built on a dark secret. Now, it's not a secret to me, but at some point, it was. And this secret is a deep flaw in the current state of the West that keeps affecting us in negative ways. The secret is that in order to defeat Hitler and the Nazis, the West allied itself with the Soviets. Stalin. An incredibly evil man and an ideology that has led to the death and suffering of more humans than the Nazis. This is just a fact, but it's so dark that we don't talk about it.
For many years as I began to study Communism and the Soviet Union I began to question why on earth did the allies align themselves with Stalin. Obviously it was for stratigic reasons. I get it. But the fact that this topic is not really discussed in our culture has had a dark effect. Now, I'm not interested in figuring out if Stalin was more evil than Hitler or if Fascism is worse that Communism. I think this misses the point. The point is that today if soneone has Nazi symbols it is very likely not gonna go well for them but Communist symbols are usually just fine. We see the ideas of Socialism discussed openly without concern. Its popular even. Fascism on the other hand is always (until recently) masked at best.
Today we are seeing more and more people openly talk about this reality, and it is a signal that the WW2 consensus is breaking. As people age out and our collective memory fades, this lie will become more visible because the mythical view of Hitler will fade. This will allow people to be more objective about viewing the decisions of the past. I don't recall the book discussing this directly, but it is an interesting connection for sure.
I recommend watching The World War II Consensus is Breaking Down by Jonathan Pageau.
https://stacker.news/items/985962
-
 @ f240be2b:00c761ba
2025-05-25 10:32:12
@ f240be2b:00c761ba
2025-05-25 10:32:12Wirtschaftswunder werden oft als mysteriöse, unvorhersehbare Phänomene dargestellt – als wären sie glückliche Zufälle oder das Ergebnis genialer Planungen. Bei näherer Betrachtung offenbart sich jedoch ein grundlegendes Muster: Diese vermeintlichen "Wunder" sind keine übernatürlichen Ereignisse, sondern das natürliche Ergebnis wirtschaftlicher Freiheit. Die Erfolgsgeschichten verschiedener Länder bestätigen diese These und zeigen, dass Wohlstand entsteht, wenn Menschen die Freiheit haben, zu handeln, zu produzieren und zu innovieren.
Das deutsche Wirtschaftswunder
Nach dem Zweiten Weltkrieg lag Deutschland in Trümmern. Die Industrieproduktion war auf ein Viertel des Vorkriegsniveaus gesunken, und Millionen Menschen lebten in Armut. Doch innerhalb weniger Jahre erlebte Westdeutschland einen beispiellosen wirtschaftlichen Aufschwung, der als "Wirtschaftswunder" in die Geschichte einging.
Der Wandel begann mit Ludwig Erhards mutiger Währungsreform und Preisfreigabe im Jahr 1948. Erhard, damals Direktor der Wirtschaftsverwaltung, schaffte Preiskontrollen ab und führte die Deutsche Mark ein. Diese Maßnahmen wurden von Besatzungsmächten und deutschen Sozialisten skeptisch betrachtet und waren zunächst unpopulär. Doch die Ergebnisse sprachen für sich: Über Nacht füllten sich die Ladenregale wieder, und die Schwarzmärkte verschwanden.
Das Kernprinzip war einfach: Erhard gab den Menschen ihre wirtschaftliche Freiheit zurück. Er schuf einen stabilen Rechtsrahmen, reduzierte staatliche Eingriffe und förderte den freien Wettbewerb. Die Sozialisten bekämpften diese Entwicklung von Anfang an, deuteten diese jedoch im Nachhinein als “soziale Marktwirtschaft” um, diese Lüge verbreiten sie noch heute sehr erfolgreich.
Die freie Marktwirtschaft erlaubte es den Deutschen, ihre unternehmerischen Fähigkeiten zu entfalten und ihre zerstörte Wirtschaft wieder aufzubauen.\ Das Ergebnis: Zwischen 1950 und 1960 wuchs das westdeutsche BIP um mehr als 8% jährlich. Die Arbeitslosigkeit sank von 11% auf unter 1%, und Deutschland wurde zu einer der führenden Exportnationen der Welt. Was als "Wunder" bezeichnet wurde, war tatsächlich die natürliche Konsequenz wiederhergestellter wirtschaftlicher Freiheit.
Chiles wirtschaftliche Transformation
Chile bietet ein weiteres eindrucksvolles Beispiel. In den frühen 1970er Jahren litt das Land unter einer Hyperinflation von 700%, einem schrumpfenden BIP und zunehmender Armut. Die Transformation begann in den späten 1970er Jahren mit tiefgreifenden Wirtschaftsreformen.
Die chilenische Regierung privatisierte Staatsunternehmen, öffnete Märkte für internationalen Handel, schuf ein stabiles Finanzsystem und führte ein innovatives Rentensystem ein. Während andere lateinamerikanische Länder mit protektionistischen Maßnahmen experimentierten, entschied sich Chile für wirtschaftliche Freiheit.
Die Ergebnisse waren beeindruckend: Zwischen 1975 und 2000 verdreifachte sich Chiles Pro-Kopf-Einkommen. Die Armutsquote sank von 45% auf unter 10%. Heute hat Chile das höchste Pro-Kopf-Einkommen in Südamerika und eine der stabilsten Wirtschaften der Region.
Mit einer gewissen Melancholie müssen wir beobachten, wie die hart erkämpften Errungenschaften Chiles allmählich in den Schatten der Vergänglichkeit gleiten. Was einst als Leuchtturm wirtschaftlicher Transformation strahlte, wird nun von den Nebeln der kollektiven Amnesie umhüllt. In dieser Dämmerung der Erinnerung finden interventionistische Strömungen erneut fruchtbaren Boden.
Dieses Phänomen ist nicht auf Chile beschränkt. Auch in Deutschland verblasst die Erinnerung an die transformative Kraft der freien Marktwirtschaft. Die Geschichte wird umgedichtet, in der wirtschaftliche Freiheit als unbarmherziger Kapitalismus karikiert wird, während staatliche Intervention als einziger Weg zur sozialen Gerechtigkeit glorifiziert wird.
Chinas große Öffnung
Im Reich der Mitte vollzog sich die vielleicht dramatischste wirtschaftliche Metamorphose unserer Zeit. Nach Jahrzehnten der Isolation und planwirtschaftlicher Starrheit öffnete China unter Deng Xiaoping vorsichtig die Tore zur wirtschaftlichen Freiheit.
Die Transformation begann in den Reisfeldern, wo Bauern erstmals seit Generationen über ihre eigene Ernte bestimmen durften. Sie setzte sich fort in den pulsierenden Sonderwirtschaftszonen, wo unternehmerische Energie auf globale Märkte traf.
Das Ergebnis war atemberaubend: Fast vier Jahrzehnte mit durchschnittlich 10 Prozent Wirtschaftswachstum jährlich – eine beispiellose Leistung in der Wirtschaftsgeschichte. Mehr als 800 Millionen Menschen überwanden die Armut und fanden den Weg in die globale Mittelschicht. Selbst die partielle Einführung wirtschaftlicher Freiheiten entfesselte eine Produktivität, die die Welt veränderte.
Die zeitlose Lektion
Das Geheimnis wirtschaftlicher Erneuerung liegt nicht in komplexen Theorien oder staatlichen Eingriffen, sondern in der einfachen Weisheit, Menschen die Freiheit zu geben, ihre Träume zu verwirklichen. Wenn wir von "Wirtschaftswundern" sprechen, verkennen wir die wahre Natur dieser Transformationen.
Sie sind keine mysteriösen Anomalien, sondern vielmehr Bestätigungen eines zeitlosen Prinzips: In der fruchtbaren Erde wirtschaftlicher Freiheit blüht der menschliche Erfindungsgeist. Diese Erkenntnis ist keine ideologische Position, sondern eine durch die Geschichte vielfach bestätigte Wahrheit.
Die Lektion dieser Erfolgsgeschichten ist sowohl schlicht als auch tiefgründig: Der Weg zu Wohlstand und menschlicher Entfaltung führt über die Anerkennung und den Schutz wirtschaftlicher Freiheiten. In dieser Erkenntnis liegt vielleicht das wahre Wunder – die beständige Kraft einer einfachen Idee, die immer wieder Leben und Hoffnung in die dunkelsten wirtschaftlichen Landschaften bringt.
Der aufsteigende Stern des Südens
Jenseits der Andenkette, wo Argentinien und Chile ihre lange Grenze teilen, entfaltet sich eine neue Erfolgsgeschichte. Mit mutigen Reformen und einer Rückbesinnung auf wirtschaftliche Freiheit erwacht dieses Land mit viel Potenzial aus seinem langen Schlummer. Was wir beobachten, ist nichts weniger als die Geburt eines neuen südamerikanischen Wirtschaftswunders – geboren aus der Erkenntnis, dass Wohlstand nicht verteilt, sondern erschaffen wird.
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ c1d77557:bf04ec8b
2025-05-25 09:46:24
@ c1d77557:bf04ec8b
2025-05-25 09:46:24No crescente universo das plataformas de jogos online, a BET7K se destaca como uma das opções mais completas e inovadoras disponíveis para o público brasileiro. Com uma interface moderna, navegação intuitiva e uma variedade de jogos que agrada desde os iniciantes até os mais experientes, a plataforma tem conquistado uma legião de fãs em todo o país. Neste artigo, vamos apresentar um panorama completo sobre a BET7K, incluindo seus principais recursos, tipos de jogos oferecidos e a experiência do jogador.
Uma Plataforma Feita Para o Público Brasileiro Desde o primeiro acesso, é possível perceber que a bet7kfoi pensada especialmente para atender às preferências do público brasileiro. O site é totalmente em português, conta com suporte ao cliente local e métodos de pagamento adaptados à realidade do país, incluindo Pix, boleto bancário e carteiras digitais. Essa acessibilidade facilita o cadastro e as transações, tornando a experiência do usuário muito mais simples e prática.
Além disso, a BET7K também oferece promoções e bônus exclusivos para jogadores brasileiros, o que contribui para um engajamento contínuo e recompensador.
Diversidade de Jogos para Todos os Gostos A variedade de jogos é um dos pontos fortes da BET7K. A plataforma reúne os principais títulos do mercado, desenvolvidos por provedores de renome internacional, garantindo gráficos de alta qualidade, jogabilidade fluida e uma experiência imersiva.
Entre os destaques estão os populares jogos de slot, que combinam sorte e emoção com temáticas variadas e recursos especiais, como rodadas grátis e multiplicadores de prêmios. Para quem prefere algo mais estratégico, a BET7K também oferece opções como pôquer, blackjack e bacará, todos em versões otimizadas para desktop e dispositivos móveis.
Além disso, os jogos de roleta ao vivo proporcionam uma experiência interativa em tempo real, permitindo que os jogadores se sintam parte de uma atmosfera de luxo e sofisticação, mesmo jogando de casa.
A Experiência do Jogador em Primeiro Lugar A BET7K investe constantemente em tecnologia e segurança para garantir que os usuários possam se divertir com tranquilidade. A plataforma utiliza criptografia avançada para proteger os dados pessoais e financeiros, além de operar com licença de funcionamento internacional, o que demonstra seu compromisso com a transparência e a legalidade.
Outro diferencial importante é o atendimento ao cliente, disponível 24 horas por dia, 7 dias por semana. Os jogadores podem entrar em contato através de chat ao vivo, e-mail ou redes sociais, sempre contando com uma equipe treinada para resolver qualquer dúvida ou problema com agilidade.
Conclusão A BET7K é uma plataforma completa, confiável e voltada para proporcionar a melhor experiência possível aos seus usuários. Seja você um iniciante curioso ou um jogador experiente em busca de novos desafios, a BET7K oferece uma combinação ideal de diversão, segurança e oportunidades de ganhos reais.
Com sua abordagem focada no público brasileiro, promoções atraentes, grande variedade de jogos e suporte de qualidade, a BET7K vem se consolidando como uma das principais referências em entretenimento online no Brasil. Se você ainda não conhece, essa é a hora perfeita para explorar tudo o que a plataforma tem a oferecer.
-
 @ c1d77557:bf04ec8b
2025-05-25 09:45:57
@ c1d77557:bf04ec8b
2025-05-25 09:45:57No universo do entretenimento online, plataformas confiáveis, seguras e repletas de opções de jogos são cada vez mais valorizadas pelos jogadores brasileiros. A Betao surge como uma dessas grandes apostas, conquistando espaço entre os amantes de jogos virtuais por oferecer uma experiência dinâmica, envolvente e repleta de oportunidades de ganhos. Com um sistema moderno, interface amigável e suporte completo ao usuário, a Betao se destaca como um verdadeiro centro de entretenimento digital.
Conhecendo a Plataforma Betao Desde o primeiro acesso, o usuário percebe o cuidado da Betao em oferecer uma navegação fluida e intuitiva. O site é organizado de maneira eficiente, com menus claros que facilitam a localização dos jogos, promoções e informações de conta. Compatível com computadores e dispositivos móveis, a plataforma é ideal para quem deseja jogar em qualquer lugar, a qualquer momento.
A segurança é um dos pontos fortes da Betao. Com sistemas de criptografia atualizados e uma política rigorosa de proteção de dados, os jogadores podem ficar tranquilos quanto à integridade de suas informações pessoais e financeiras. Além disso, o suporte técnico é ágil e atencioso, pronto para resolver qualquer dúvida ou dificuldade de forma rápida e eficaz.
Variedade de Jogos para Todos os Estilos A grande diversidade de jogos é outro atrativo da Betao. A plataforma reúne títulos que atendem aos mais variados perfis de jogadores, desde os iniciantes até os mais experientes. Entre as opções, estão os tradicionais jogos de cartas, como pôquer e bacará, além de roletas e slots com temáticas criativas e gráficos de alta qualidade.
Os slots, em especial, são um grande sucesso na Betao. Com centenas de títulos disponíveis, os jogadores encontram desde opções clássicas com três rolos até versões modernas com múltiplas linhas de pagamento e recursos especiais. Muitos desses jogos oferecem rodadas grátis, multiplicadores e bônus interativos que aumentam ainda mais a emoção.
A Betao também oferece modalidades com crupiês ao vivo, criando uma atmosfera realista e interativa, onde o jogador pode se sentir em uma verdadeira sala de jogos, mesmo estando em casa. Essa funcionalidade aumenta a imersão e proporciona uma experiência diferenciada e sofisticada.
Experiência do Jogador: Simplicidade e Emoção O foco principal da Betao é proporcionar ao usuário uma jornada divertida e segura. Desde o cadastro, que é simples e rápido, até o processo de depósito e saque — que aceita os métodos de pagamento mais populares entre os brasileiros — tudo foi pensado para facilitar a vida do jogador.
As promoções constantes também são um atrativo à parte. A Betao oferece bônus de boas-vindas, campanhas sazonais e programas de fidelidade que recompensam os jogadores mais ativos com prêmios exclusivos. Isso cria uma sensação de valorização e motiva os usuários a retornarem sempre.
Outro ponto positivo é a transparência da plataforma. As regras dos jogos, os critérios para os bônus e os termos de uso estão sempre disponíveis de forma clara, reforçando a confiabilidade da Betao.
Conclusão A Betao é mais do que uma simples plataforma de jogos: é um ambiente completo de entretenimento digital, onde a diversão se alia à segurança e à inovação. Com uma oferta ampla de jogos, suporte eficiente e promoções atrativas, a Betao vem ganhando cada vez mais a preferência dos brasileiros que buscam emoção e praticidade em um só lugar. Se você procura uma plataforma moderna, confiável e repleta de possibilidades, a Betao é, sem dúvida, a escolha certa para sua próxima aventura online.
-
 @ 2b24a1fa:17750f64
2025-05-25 09:42:49
@ 2b24a1fa:17750f64
2025-05-25 09:42:49Eine Stunde Klassik! Der Münchner Pianist und "Musikdurchdringer" Jürgen Plich stellt jeden Dienstag um 20 Uhr große klassische Musik vor. Er teilt seine Hör- und Spielerfahrung und seine persönliche Sicht auf die Meisterwerke. Er spielt selbst besondere, unbekannte Aufnahmen, erklärt, warum die Musik so und nicht anders klingt und hat eine Menge aus dem Leben der Komponisten zu erzählen.
https://soundcloud.com/radiomuenchen/eine-stunde-klassik-opus-eins?
Sonntags um 10 Uhr in der Wiederholung.
-
 @ 6389be64:ef439d32
2025-01-16 15:44:06
@ 6389be64:ef439d32
2025-01-16 15:44:06Black Locust can grow up to 170 ft tall
Grows 3-4 ft. per year
Native to North America
Cold hardy in zones 3 to 8

Firewood
- BLT wood, on a pound for pound basis is roughly half that of Anthracite Coal
- Since its growth is fast, firewood can be plentiful
Timber

- Rot resistant due to a naturally produced robinin in the wood
- 100 year life span in full soil contact! (better than cedar performance)
- Fence posts
- Outdoor furniture
- Outdoor decking
- Sustainable due to its fast growth and spread
- Can be coppiced (cut to the ground)
- Can be pollarded (cut above ground)
- Its dense wood makes durable tool handles, boxes (tool), and furniture
- The wood is tougher than hickory, which is tougher than hard maple, which is tougher than oak.
- A very low rate of expansion and contraction
- Hardwood flooring
- The highest tensile beam strength of any American tree
- The wood is beautiful
Legume
- Nitrogen fixer
- Fixes the same amount of nitrogen per acre as is needed for 200-bushel/acre corn
- Black walnuts inter-planted with locust as “nurse” trees were shown to rapidly increase their growth [[Clark, Paul M., and Robert D. Williams. (1978) Black walnut growth increased when interplanted with nitrogen-fixing shrubs and trees. Proceedings of the Indiana Academy of Science, vol. 88, pp. 88-91.]]
Bees

- The edible flower clusters are also a top food source for honey bees
Shade Provider

- Its light, airy overstory provides dappled shade
- Planted on the west side of a garden it provides relief during the hottest part of the day
- (nitrogen provider)
- Planted on the west side of a house, its quick growth soon shades that side from the sun
Wind-break

- Fast growth plus it's feathery foliage reduces wind for animals, crops, and shelters
Fodder
- Over 20% crude protein
- 4.1 kcal/g of energy
- Baertsche, S.R, M.T. Yokoyama, and J.W. Hanover (1986) Short rotation, hardwood tree biomass as potential ruminant feed-chemical composition, nylon bag ruminal degradation and ensilement of selected species. J. Animal Sci. 63 2028-2043
-
 @ 9c9d2765:16f8c2c2
2025-05-25 08:26:53
@ 9c9d2765:16f8c2c2
2025-05-25 08:26:53CHAPTER TWENTY EIGHT
“He’s not just surviving,” Helen hissed through clenched teeth, her heels striking the marble floors of her penthouse like war drums. “He’s thriving, and it’s infuriating.”
Mark leaned against the window, watching the evening lights of the city shimmer beneath them. “That transparency stunt he pulled? Genius,” he muttered. “It shut down every accusation we tried to plant before it could sprout.”
Helen turned abruptly. “Then we change the terrain. If he’s building on trust, we flood him with betrayal. We turn his loyalists into doubters.”
Mark raised a brow. “And how do you propose we do that?”
She walked over to the coffee table, picked up a manila envelope, and tossed it onto his lap. It opened with a quiet rustle, revealing photos some staged, others manipulated of James in ambiguous meetings, with headlines drafted in bold red: “JP President Linked to Foreign Espionage?”, “Undisclosed Meetings with Rival Companies.”
“These go live next week,” Helen said coldly. “And if we can’t break his empire from the outside, we’ll corrode it from within.”
Meanwhile, across the city, James stood in the training hall of JP Enterprises, overseeing a leadership seminar. The room brimmed with young professionals, eager minds molded by his vision. He paced slowly, hands behind his back.
“Leadership isn’t about dominance,” he said, his voice calm yet commanding. “It’s about service. True power lies in how many people rise because of you, not how many kneel before you.”
Applause followed, but James’s mind drifted. The storm was coming and he could feel it. The shadows hadn’t retreated; they’d merely been biding their time. But what Helen and Mark underestimated was the strength of what he’d built. This time, he wasn’t alone.
After the seminar, he returned to his office where Rita and Charles were already waiting.
“They’re not backing down,” Rita said, placing a thick fillet on his desk. “Our cybersecurity team intercepted metadata from an anonymous article scheduled to be released next Monday. It traces back to one of Helen’s known shell accounts.”
Charles leaned forward. “They’re targeting your integrity again, James. This time with international implications. If this goes public, it could trigger a full-scale investigation even if the claims are false.”
James took a deep breath. “Then it’s time to activate Project Aegis.”
Rita’s eyes widened. “You mean?”
“Yes,” James affirmed. “Full legal exposure. Every executive, every document, every deal for the last five years. We publish it ourselves before they can twist it.”
Charles nodded slowly, admiration gleaming in his eyes. “You're not just playing defense anymore.”
“No,” James said, his voice resolute. “I’m done playing. It’s time they learn integrity is not a weakness. It’s my greatest strength.”
That same night, Helen and Mark received a notification that sent chills down their spines. Every major news outlet was now broadcasting a preemptive report by JP Enterprises: “A Legacy in the Light JP Enterprises Opens Vaults to Public Scrutiny”. The article was followed by interviews with board members, stakeholders, and long-time employees all affirming James’s character and transparency.
Helen clenched her jaw, watching the screen with cold fury. “He’s rewriting the rules…” she muttered.
“No,” Mark whispered. “He’s building a world where we don’t exist.”
In the quiet of his penthouse office, James stood by the tall glass windows, the city’s nightscape shimmering beneath a sky painted in indigo hues. A cup of untouched coffee sat on the mahogany desk behind him. His reflection merged with the sprawling lights of a man once discarded, now the pillar of a corporate empire.
Despite the outward calm, James’s mind churned like a brewing storm. The recent smear campaign, although crushed by his proactive transparency, had planted seeds of uncertainty in some corners of the public. He knew Helen and Mark were far from surrendering. Their strategy had evolved into psychological warfare planting doubt, sowing division, manipulating perception.
“It’s time to start setting traps of our own,” he murmured under his breath.
He turned from the window as Charles entered the room, holding a tablet.
“It’s worse than we anticipated,” Charles began, concerned with furrowing his brow. “They’ve been funneling money through offshore accounts, paying journalists, bloggers, even some minor influencers to perpetuate false narratives. They’re not just trying to ruin your reputation, they're orchestrating a hostile takeover.”
James exhaled, slowly walking to his desk. “Then we play them at their own game but with honor. I want a full audit of every subsidiary tied to Ray Enterprises and Helen’s private ventures. Any shadow move they’ve made, I want it exposed legally, publicly, and without a hint of impropriety.”
Charles gave a resolute nod. “I’ll get our internal compliance team on it tonight.”
Meanwhile, across town, Helen sat before a marble fireplace in her lavish estate, her fingers tapping impatiently against a crystal glass of wine. Mark sat across from her, scrolling through dozens of negative online articles none of which were about James.
“He flipped the story again,” Mark said bitterly. “People are actually praising him for his transparency. Investors are swarming back. Even media outlets we bribed are retracting their pieces just to avoid a lawsuit.”
Helen’s eyes burned with fury. “Then we escalate. If he wants to play hero, we’ll paint him as a fraud who built an empire on stolen foundations. Everyone has a skeleton buried deep. We just need to find his.”
Back at JP Enterprises, James was meeting with Rita and a trusted cybersecurity analyst, a sharp-eyed woman named Lilian.
“We’ve traced an internal breach,” Lilian reported. “One of the forwarded articles that nearly made it to international outlets was leaked from someone inside our media division.”
Rita frowned. “Tracy.”
James nodded slowly. “She’s the thread connecting Mark and Helen’s plots. But she’s not alone. There’s another… more subtle player behind all this. And I intend to flush them out without alerting the rats.”
The next day, James called a confidential press meeting. With calm confidence, he unveiled The Integrity Initiative, a new transparency program offering unprecedented access to the inner workings of JP Enterprises for all stakeholders.
“We’ve built this company on the belief that truth withstands scrutiny,” he said, his voice echoing through the hall. “We have nothing to hide and for those trying to destroy us with lies, we welcome your eyes. Because when the truth stands tall, shadows disappear.”
The speech went viral within hours. Critics became advocates. Doubters became loyalists. And for Mark and Helen, the walls began to close in faster than they expected.
It had been two days since James’s press conference, and the atmosphere in the city’s business sphere had shifted noticeably. Conversations once filled with doubt and suspicion about JP Enterprises now carried admiration and curiosity. The sudden introduction of The Integrity Initiative had stirred an entirely new level of respect for the company and for James as its helmsman.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 000002de:c05780a7
2025-05-21 17:42:27
@ 000002de:c05780a7
2025-05-21 17:42:27I've been trying out Arch Linux again and the thing that always surprises me is pacman. The way it works seems so unintuitive to me coming from the apt, yum, and dnf worlds.
I know I will get it and it will become internalized but I just wonder what the designer was thinking when making the flags/commands.
https://stacker.news/items/985808
-
 @ 3283ef81:0a531a33
2025-05-25 09:20:07
@ 3283ef81:0a531a33
2025-05-25 09:20:07Phasellus erat metus, suscipit et nisi a, dignissim luctus risus\ Nam eleifend aliquet aliquam
Curabitur vulputate velit elit, sit amet euismod nibh venenatis et
-
 @ 9c9d2765:16f8c2c2
2025-05-25 08:14:32
@ 9c9d2765:16f8c2c2
2025-05-25 08:14:32CHAPTER TWENTY SEVEN “We’re finished,” she snapped, pacing furiously. “They’ve locked every door. We’ve been blacklisted by every reputable firm in the city. No one's taking our calls, and now the tax authorities are sniffing around!”
Mark stood slowly, still holding the glass. “It’s all because of him,” he growled. “James. That street rat turned king. He’s poisoned the whole industry against us.”
Helen scoffed. “He didn’t poison it. He conquered it. You and I? We underestimated him. We saw rags and never imagined the gold beneath.”
There was a moment of raw, uncomfortable silence.
“And now,” she added bitterly, “he owns not just the Ray company but the story. The people adore him. Every misstep we make adds to his legend.”
Mark turned away, the fury in his chest simmering just below the surface. “Then maybe it’s time we stop playing by his rules.”
Helen raised an eyebrow. “What are you thinking?”
“Something permanent,” he said coldly. “Something that’ll make the city question his legacy. We won’t touch him directly. But we’ll dismantle everything around him his alliances, his investors, his trust.”
Meanwhile, at JP Enterprises, James was meeting with his board members. The mood was triumphant. Contracts were flowing in from across the nation. Investors from overseas were lining up to collaborate. JP Enterprises was no longer a local giant, it was becoming a global force.
As the board meeting wrapped up, Charles approached James with a discreet file.
“We’ve uncovered something,” he said in a hushed tone. “Helen and Mark have begun contacting shell companies. They’re orchestrating something through offshore accounts. It’s not clear yet, but they’re moving funds and people.”
James took the file, flipping through the pages with a calm intensity. “They never learn,” he murmured. “Desperation is a dangerous motivator.”
Charles nodded. “Shall we alert the authorities?”
James paused. “Not yet. Let them think they’re getting away with it. Let them build the stage. And when the curtains rise, we’ll pull the spotlight on them ourselves.”
Outside, the sky turned amber as dusk crept over the horizon. Somewhere in the city, Mark and Helen were plotting their next move. But in the heart of JP Enterprises, James was already five steps ahead.
The night veiled the city in a silvery calm, but within the walls of an abandoned warehouse at the edge of town, shadows danced beneath flickering fluorescent lights. Mark and Helen stood amidst crates of outdated office furniture and rusted metal, far removed from the lavish boardrooms they once commanded. Their pride, now fragments, echoed in every creak of the floor beneath them.
“We’ve traced every name that still owes us favors,” Mark said, unfolding a large sheet of paper across a makeshift table. “This is our web. Media contacts. Shell consultants. A few digital mercenaries.”
Helen leaned over the table, eyes scanning the diagram. “It’s not about hitting him,” she whispered. “It’s about bleeding his legacy. Bit by bit. We drown him in whispers, not weapons.”
Their plan was insidious smear campaigns seeded in anonymous blogs, fabricated audits from paid ‘inspectors,’ leaks of doctored company records, and the reawakening of James’s past, even if the ghosts had already been proven false. They would question every victory he had, casting shadows over every triumph. If they couldn’t win, they would ruin the game.
Meanwhile, back at JP Enterprises, James sat in his office high above the city. The glass walls gave him a breathtaking view, but his gaze was introspective. His mind wandered through recent events the betrayal, the accusations, the painful resurgence of a forgotten past. But what stood out most was not the malice of others. It was how he had endured.
Charles entered the office, a slight knock preceding him. “We’ve secured the last two tech firms you were eyeing. Their CEOs are prepared to sign exclusive partnerships. Also, the board wants to recognize you officially as Global CEO during next month’s summit.”
James smiled faintly, though his eyes retained a solemn hue. “Good. But there’s something more important.” He turned his laptop around, displaying a series of anonymous online threads riddled with false claims and slander.
“They’ve begun,” he said softly. “Helen and Mark are orchestrating a campaign to rot our foundation from the inside out.”
Charles's expression darkened. “Should I initiate a counter-sweep?”
James shook his head. “No. We don’t fight shadows with swords. We fight them with light.” He paused, then added, “I want full transparency reports across every department. I want our investors to see our books before they ask. I want our work to speak so loudly, their lies get drowned out.”
In a conference the following morning, James stood before hundreds of stakeholders and partners, unveiling a revolutionary corporate transparency portal. Real-time audits, project status updates, and salary distributions were now accessible to all registered partners. The press called it “the death of corporate secrecy.”
While Mark and Helen were weaving illusions, James was showcasing reality.
Yet in the shadows, Helen grew more frustrated.
“He’s not cracking!” she shouted, hurling a tablet against the floor. “How is he still standing?”
Mark sat, quiet for once, rubbing his temples. “Because he’s not the man we knew. He’s not the beggar we mocked. He’s become… untouchable.”
Helen turned, her eyes blazing. “Then we don’t touch him. We find someone he cares about. We make him feel vulnerable again.”
Mark didn’t speak, but the silence between them felt like a pact being sealed.
Back at JP Enterprises, James met with Rita. Her sharpness and integrity had restored much of the company’s cultural fabric. He trusted her, more than most. And as they walked the office floors together, they discussed not just projects, but the future that would soon test every bond, every alliance.
-
 @ 6389be64:ef439d32
2025-01-13 21:50:59
@ 6389be64:ef439d32
2025-01-13 21:50:59Bitcoin is more than money, more than an asset, and more than a store of value. Bitcoin is a Prime Mover, an enabler and it ignites imaginations. It certainly fueled an idea in my mind. The idea integrates sensors, computational prowess, actuated machinery, power conversion, and electronic communications to form an autonomous, machined creature roaming forests and harvesting the most widespread and least energy-dense fuel source available. I call it the Forest Walker and it eats wood, and mines Bitcoin.
I know what you're thinking. Why not just put Bitcoin mining rigs where they belong: in a hosted facility sporting electricity from energy-dense fuels like natural gas, climate-controlled with excellent data piping in and out? Why go to all the trouble building a robot that digests wood creating flammable gasses fueling an engine to run a generator powering Bitcoin miners? It's all about synergy.
Bitcoin mining enables the realization of multiple, seemingly unrelated, yet useful activities. Activities considered un-profitable if not for Bitcoin as the Prime Mover. This is much more than simply mining the greatest asset ever conceived by humankind. It’s about the power of synergy, which Bitcoin plays only one of many roles. The synergy created by this system can stabilize forests' fire ecology while generating multiple income streams. That’s the realistic goal here and requires a brief history of American Forest management before continuing.
Smokey The Bear
In 1944, the Smokey Bear Wildfire Prevention Campaign began in the United States. “Only YOU can prevent forest fires” remains the refrain of the Ad Council’s longest running campaign. The Ad Council is a U.S. non-profit set up by the American Association of Advertising Agencies and the Association of National Advertisers in 1942. It would seem that the U.S. Department of the Interior was concerned about pesky forest fires and wanted them to stop. So, alongside a national policy of extreme fire suppression they enlisted the entire U.S. population to get onboard via the Ad Council and it worked. Forest fires were almost obliterated and everyone was happy, right? Wrong.
Smokey is a fantastically successful bear so forest fires became so few for so long that the fuel load - dead wood - in forests has become very heavy. So heavy that when a fire happens (and they always happen) it destroys everything in its path because the more fuel there is the hotter that fire becomes. Trees, bushes, shrubs, and all other plant life cannot escape destruction (not to mention homes and businesses). The soil microbiology doesn’t escape either as it is burned away even in deeper soils. To add insult to injury, hydrophobic waxy residues condense on the soil surface, forcing water to travel over the ground rather than through it eroding forest soils. Good job, Smokey. Well done, Sir!
Most terrestrial ecologies are “fire ecologies”. Fire is a part of these systems’ fuel load and pest management. Before we pretended to “manage” millions of acres of forest, fires raged over the world, rarely damaging forests. The fuel load was always too light to generate fires hot enough to moonscape mountainsides. Fires simply burned off the minor amounts of fuel accumulated since the fire before. The lighter heat, smoke, and other combustion gasses suppressed pests, keeping them in check and the smoke condensed into a plant growth accelerant called wood vinegar, not a waxy cap on the soil. These fires also cleared out weak undergrowth, cycled minerals, and thinned the forest canopy, allowing sunlight to penetrate to the forest floor. Without a fire’s heat, many pine tree species can’t sow their seed. The heat is required to open the cones (the seed bearing structure) of Spruce, Cypress, Sequoia, Jack Pine, Lodgepole Pine and many more. Without fire forests can’t have babies. The idea was to protect the forests, and it isn't working.
So, in a world of fire, what does an ally look like and what does it do?
Meet The Forest Walker
For the Forest Walker to work as a mobile, autonomous unit, a solid platform that can carry several hundred pounds is required. It so happens this chassis already exists but shelved.
Introducing the Legged Squad Support System (LS3). A joint project between Boston Dynamics, DARPA, and the United States Marine Corps, the quadrupedal robot is the size of a cow, can carry 400 pounds (180 kg) of equipment, negotiate challenging terrain, and operate for 24 hours before needing to refuel. Yes, it had an engine. Abandoned in 2015, the thing was too noisy for military deployment and maintenance "under fire" is never a high-quality idea. However, we can rebuild it to act as a platform for the Forest Walker; albeit with serious alterations. It would need to be bigger, probably. Carry more weight? Definitely. Maybe replace structural metal with carbon fiber and redesign much as 3D printable parts for more effective maintenance.
The original system has a top operational speed of 8 miles per hour. For our purposes, it only needs to move about as fast as a grazing ruminant. Without the hammering vibrations of galloping into battle, shocks of exploding mortars, and drunken soldiers playing "Wrangler of Steel Machines", time between failures should be much longer and the overall energy consumption much lower. The LS3 is a solid platform to build upon. Now it just needs to be pulled out of the mothballs, and completely refitted with outboard equipment.
The Small Branch Chipper
When I say “Forest fuel load” I mean the dead, carbon containing litter on the forest floor. Duff (leaves), fine-woody debris (small branches), and coarse woody debris (logs) are the fuel that feeds forest fires. Walk through any forest in the United States today and you will see quite a lot of these materials. Too much, as I have described. Some of these fuel loads can be 8 tons per acre in pine and hardwood forests and up to 16 tons per acre at active logging sites. That’s some big wood and the more that collects, the more combustible danger to the forest it represents. It also provides a technically unlimited fuel supply for the Forest Walker system.
The problem is that this detritus has to be chewed into pieces that are easily ingestible by the system for the gasification process (we’ll get to that step in a minute). What we need is a wood chipper attached to the chassis (the LS3); its “mouth”.
A small wood chipper handling material up to 2.5 - 3.0 inches (6.3 - 7.6 cm) in diameter would eliminate a substantial amount of fuel. There is no reason for Forest Walker to remove fallen trees. It wouldn’t have to in order to make a real difference. It need only identify appropriately sized branches and grab them. Once loaded into the chipper’s intake hopper for further processing, the beast can immediately look for more “food”. This is essentially kindling that would help ignite larger logs. If it’s all consumed by Forest Walker, then it’s not present to promote an aggravated conflagration.
I have glossed over an obvious question: How does Forest Walker see and identify branches and such? LiDaR (Light Detection and Ranging) attached to Forest Walker images the local area and feed those data to onboard computers for processing. Maybe AI plays a role. Maybe simple machine learning can do the trick. One thing is for certain: being able to identify a stick and cause robotic appendages to pick it up is not impossible.
Great! We now have a quadrupedal robot autonomously identifying and “eating” dead branches and other light, combustible materials. Whilst strolling through the forest, depleting future fires of combustibles, Forest Walker has already performed a major function of this system: making the forest safer. It's time to convert this low-density fuel into a high-density fuel Forest Walker can leverage. Enter the gasification process.
The Gassifier
The gasifier is the heart of the entire system; it’s where low-density fuel becomes the high-density fuel that powers the entire system. Biochar and wood vinegar are process wastes and I’ll discuss why both are powerful soil amendments in a moment, but first, what’s gasification?
Reacting shredded carbonaceous material at high temperatures in a low or no oxygen environment converts the biomass into biochar, wood vinegar, heat, and Synthesis Gas (Syngas). Syngas consists primarily of hydrogen, carbon monoxide, and methane. All of which are extremely useful fuels in a gaseous state. Part of this gas is used to heat the input biomass and keep the reaction temperature constant while the internal combustion engine that drives the generator to produce electrical power consumes the rest.
Critically, this gasification process is “continuous feed”. Forest Walker must intake biomass from the chipper, process it to fuel, and dump the waste (CO2, heat, biochar, and wood vinegar) continuously. It cannot stop. Everything about this system depends upon this continual grazing, digestion, and excretion of wastes just as a ruminal does. And, like a ruminant, all waste products enhance the local environment.
When I first heard of gasification, I didn’t believe that it was real. Running an electric generator from burning wood seemed more akin to “conspiracy fantasy” than science. Not only is gasification real, it’s ancient technology. A man named Dean Clayton first started experiments on gasification in 1699 and in 1901 gasification was used to power a vehicle. By the end of World War II, there were 500,000 Syngas powered vehicles in Germany alone because of fossil fuel rationing during the war. The global gasification market was $480 billion in 2022 and projected to be as much as $700 billion by 2030 (Vantage Market Research). Gasification technology is the best choice to power the Forest Walker because it’s self-contained and we want its waste products.
Biochar: The Waste
Biochar (AKA agricultural charcoal) is fairly simple: it’s almost pure, solid carbon that resembles charcoal. Its porous nature packs large surface areas into small, 3 dimensional nuggets. Devoid of most other chemistry, like hydrocarbons (methane) and ash (minerals), biochar is extremely lightweight. Do not confuse it with the charcoal you buy for your grill. Biochar doesn’t make good grilling charcoal because it would burn too rapidly as it does not contain the multitude of flammable components that charcoal does. Biochar has several other good use cases. Water filtration, water retention, nutrient retention, providing habitat for microscopic soil organisms, and carbon sequestration are the main ones that we are concerned with here.
Carbon has an amazing ability to adsorb (substances stick to and accumulate on the surface of an object) manifold chemistries. Water, nutrients, and pollutants tightly bind to carbon in this format. So, biochar makes a respectable filter and acts as a “battery” of water and nutrients in soils. Biochar adsorbs and holds on to seven times its weight in water. Soil containing biochar is more drought resilient than soil without it. Adsorbed nutrients, tightly sequestered alongside water, get released only as plants need them. Plants must excrete protons (H+) from their roots to disgorge water or positively charged nutrients from the biochar's surface; it's an active process.
Biochar’s surface area (where adsorption happens) can be 500 square meters per gram or more. That is 10% larger than an official NBA basketball court for every gram of biochar. Biochar’s abundant surface area builds protective habitats for soil microbes like fungi and bacteria and many are critical for the health and productivity of the soil itself.
The “carbon sequestration” component of biochar comes into play where “carbon credits” are concerned. There is a financial market for carbon. Not leveraging that market for revenue is foolish. I am climate agnostic. All I care about is that once solid carbon is inside the soil, it will stay there for thousands of years, imparting drought resiliency, fertility collection, nutrient buffering, and release for that time span. I simply want as much solid carbon in the soil because of the undeniably positive effects it has, regardless of any climactic considerations.
Wood Vinegar: More Waste
Another by-product of the gasification process is wood vinegar (Pyroligneous acid). If you have ever seen Liquid Smoke in the grocery store, then you have seen wood vinegar. Principally composed of acetic acid, acetone, and methanol wood vinegar also contains ~200 other organic compounds. It would seem intuitive that condensed, liquefied wood smoke would at least be bad for the health of all living things if not downright carcinogenic. The counter intuition wins the day, however. Wood vinegar has been used by humans for a very long time to promote digestion, bowel, and liver health; combat diarrhea and vomiting; calm peptic ulcers and regulate cholesterol levels; and a host of other benefits.
For centuries humans have annually burned off hundreds of thousands of square miles of pasture, grassland, forest, and every other conceivable terrestrial ecosystem. Why is this done? After every burn, one thing becomes obvious: the almost supernatural growth these ecosystems exhibit after the burn. How? Wood vinegar is a component of this growth. Even in open burns, smoke condenses and infiltrates the soil. That is when wood vinegar shows its quality.
This stuff beefs up not only general plant growth but seed germination as well and possesses many other qualities that are beneficial to plants. It’s a pesticide, fungicide, promotes beneficial soil microorganisms, enhances nutrient uptake, and imparts disease resistance. I am barely touching a long list of attributes here, but you want wood vinegar in your soil (alongside biochar because it adsorbs wood vinegar as well).
The Internal Combustion Engine
Conversion of grazed forage to chemical, then mechanical, and then electrical energy completes the cycle. The ICE (Internal Combustion Engine) converts the gaseous fuel output from the gasifier to mechanical energy, heat, water vapor, and CO2. It’s the mechanical energy of a rotating drive shaft that we want. That rotation drives the electric generator, which is the heartbeat we need to bring this monster to life. Luckily for us, combined internal combustion engine and generator packages are ubiquitous, delivering a defined energy output given a constant fuel input. It’s the simplest part of the system.
The obvious question here is whether the amount of syngas provided by the gasification process will provide enough energy to generate enough electrons to run the entire system or not. While I have no doubt the energy produced will run Forest Walker's main systems the question is really about the electrons left over. Will it be enough to run the Bitcoin mining aspect of the system? Everything is a budget.
CO2 Production For Growth
Plants are lollipops. No matter if it’s a tree or a bush or a shrubbery, the entire thing is mostly sugar in various formats but mostly long chain carbohydrates like lignin and cellulose. Plants need three things to make sugar: CO2, H2O and light. In a forest, where tree densities can be quite high, CO2 availability becomes a limiting growth factor. It’d be in the forest interests to have more available CO2 providing for various sugar formation providing the organism with food and structure.
An odd thing about tree leaves, the openings that allow gasses like the ever searched for CO2 are on the bottom of the leaf (these are called stomata). Not many stomata are topside. This suggests that trees and bushes have evolved to find gasses like CO2 from below, not above and this further suggests CO2 might be in higher concentrations nearer the soil.
The soil life (bacterial, fungi etc.) is constantly producing enormous amounts of CO2 and it would stay in the soil forever (eventually killing the very soil life that produces it) if not for tidal forces. Water is everywhere and whether in pools, lakes, oceans or distributed in “moist” soils water moves towards to the moon. The water in the soil and also in the water tables below the soil rise toward the surface every day. When the water rises, it expels the accumulated gasses in the soil into the atmosphere and it’s mostly CO2. It’s a good bet on how leaves developed high populations of stomata on the underside of leaves. As the water relaxes (the tide goes out) it sucks oxygenated air back into the soil to continue the functions of soil life respiration. The soil “breathes” albeit slowly.
The gasses produced by the Forest Walker’s internal combustion engine consist primarily of CO2 and H2O. Combusting sugars produce the same gasses that are needed to construct the sugars because the universe is funny like that. The Forest Walker is constantly laying down these critical construction elements right where the trees need them: close to the ground to be gobbled up by the trees.
The Branch Drones
During the last ice age, giant mammals populated North America - forests and otherwise. Mastodons, woolly mammoths, rhinos, short-faced bears, steppe bison, caribou, musk ox, giant beavers, camels, gigantic ground-dwelling sloths, glyptodons, and dire wolves were everywhere. Many were ten to fifteen feet tall. As they crashed through forests, they would effectively cleave off dead side-branches of trees, halting the spread of a ground-based fire migrating into the tree crown ("laddering") which is a death knell for a forest.
These animals are all extinct now and forests no longer have any manner of pruning services. But, if we build drones fitted with cutting implements like saws and loppers, optical cameras and AI trained to discern dead branches from living ones, these drones could effectively take over pruning services by identifying, cutting, and dropping to the forest floor, dead branches. The dropped branches simply get collected by the Forest Walker as part of its continual mission.
The drones dock on the back of the Forest Walker to recharge their batteries when low. The whole scene would look like a grazing cow with some flies bothering it. This activity breaks the link between a relatively cool ground based fire and the tree crowns and is a vital element in forest fire control.
The Bitcoin Miner
Mining is one of four monetary incentive models, making this system a possibility for development. The other three are US Dept. of the Interior, township, county, and electrical utility company easement contracts for fuel load management, global carbon credits trading, and data set sales. All the above depends on obvious questions getting answered. I will list some obvious ones, but this is not an engineering document and is not the place for spreadsheets. How much Bitcoin one Forest Walker can mine depends on everything else. What amount of biomass can we process? Will that biomass flow enough Syngas to keep the lights on? Can the chassis support enough mining ASICs and supporting infrastructure? What does that weigh and will it affect field performance? How much power can the AC generator produce?
Other questions that are more philosophical persist. Even if a single Forest Walker can only mine scant amounts of BTC per day, that pales to how much fuel material it can process into biochar. We are talking about millions upon millions of forested acres in need of fuel load management. What can a single Forest Walker do? I am not thinking in singular terms. The Forest Walker must operate as a fleet. What could 50 do? 500?
What is it worth providing a service to the world by managing forest fuel loads? Providing proof of work to the global monetary system? Seeding soil with drought and nutrient resilience by the excretion, over time, of carbon by the ton? What did the last forest fire cost?
The Mesh Network
What could be better than one bitcoin mining, carbon sequestering, forest fire squelching, soil amending behemoth? Thousands of them, but then they would need to be able to talk to each other to coordinate position, data handling, etc. Fitted with a mesh networking device, like goTenna or Meshtastic LoRa equipment enables each Forest Walker to communicate with each other.
Now we have an interconnected fleet of Forest Walkers relaying data to each other and more importantly, aggregating all of that to the last link in the chain for uplink. Well, at least Bitcoin mining data. Since block data is lightweight, transmission of these data via mesh networking in fairly close quartered environs is more than doable. So, how does data transmit to the Bitcoin Network? How do the Forest Walkers get the previous block data necessary to execute on mining?
Back To The Chain
Getting Bitcoin block data to and from the network is the last puzzle piece. The standing presumption here is that wherever a Forest Walker fleet is operating, it is NOT within cell tower range. We further presume that the nearest Walmart Wi-Fi is hours away. Enter the Blockstream Satellite or something like it.
A separate, ground-based drone will have two jobs: To stay as close to the nearest Forest Walker as it can and to provide an antennae for either terrestrial or orbital data uplink. Bitcoin-centric data is transmitted to the "uplink drone" via the mesh networked transmitters and then sent on to the uplink and the whole flow goes in the opposite direction as well; many to one and one to many.
We cannot transmit data to the Blockstream satellite, and it will be up to Blockstream and companies like it to provide uplink capabilities in the future and I don't doubt they will. Starlink you say? What’s stopping that company from filtering out block data? Nothing because it’s Starlink’s system and they could decide to censor these data. It seems we may have a problem sending and receiving Bitcoin data in back country environs.
But, then again, the utility of this system in staunching the fuel load that creates forest fires is extremely useful around forested communities and many have fiber, Wi-Fi and cell towers. These communities could be a welcoming ground zero for first deployments of the Forest Walker system by the home and business owners seeking fire repression. In the best way, Bitcoin subsidizes the safety of the communities.
Sensor Packages
LiDaR
The benefit of having a Forest Walker fleet strolling through the forest is the never ending opportunity for data gathering. A plethora of deployable sensors gathering hyper-accurate data on everything from temperature to topography is yet another revenue generator. Data is valuable and the Forest Walker could generate data sales to various government entities and private concerns.
LiDaR (Light Detection and Ranging) can map topography, perform biomass assessment, comparative soil erosion analysis, etc. It so happens that the Forest Walker’s ability to “see,” to navigate about its surroundings, is LiDaR driven and since it’s already being used, we can get double duty by harvesting that data for later use. By using a laser to send out light pulses and measuring the time it takes for the reflection of those pulses to return, very detailed data sets incrementally build up. Eventually, as enough data about a certain area becomes available, the data becomes useful and valuable.
Forestry concerns, both private and public, often use LiDaR to build 3D models of tree stands to assess the amount of harvest-able lumber in entire sections of forest. Consulting companies offering these services charge anywhere from several hundred to several thousand dollars per square kilometer for such services. A Forest Walker generating such assessments on the fly while performing its other functions is a multi-disciplinary approach to revenue generation.
pH, Soil Moisture, and Cation Exchange Sensing
The Forest Walker is quadrupedal, so there are four contact points to the soil. Why not get a pH data point for every step it takes? We can also gather soil moisture data and cation exchange capacities at unheard of densities because of sampling occurring on the fly during commission of the system’s other duties. No one is going to build a machine to do pH testing of vast tracts of forest soils, but that doesn’t make the data collected from such an endeavor valueless. Since the Forest Walker serves many functions at once, a multitude of data products can add to the return on investment component.
Weather Data
Temperature, humidity, pressure, and even data like evapotranspiration gathered at high densities on broad acre scales have untold value and because the sensors are lightweight and don’t require large power budgets, they come along for the ride at little cost. But, just like the old mantra, “gas, grass, or ass, nobody rides for free”, these sensors provide potential revenue benefits just by them being present.
I’ve touched on just a few data genres here. In fact, the question for universities, governmental bodies, and other institutions becomes, “How much will you pay us to attach your sensor payload to the Forest Walker?”
Noise Suppression
Only you can prevent Metallica filling the surrounds with 120 dB of sound. Easy enough, just turn the car stereo off. But what of a fleet of 50 Forest Walkers operating in the backcountry or near a township? 500? 5000? Each one has a wood chipper, an internal combustion engine, hydraulic pumps, actuators, and more cooling fans than you can shake a stick at. It’s a walking, screaming fire-breathing dragon operating continuously, day and night, twenty-four hours a day, three hundred sixty-five days a year. The sound will negatively affect all living things and that impacts behaviors. Serious engineering consideration and prowess must deliver a silencing blow to the major issue of noise.
It would be foolish to think that a fleet of Forest Walkers could be silent, but if not a major design consideration, then the entire idea is dead on arrival. Townships would not allow them to operate even if they solved the problem of widespread fuel load and neither would governmental entities, and rightly so. Nothing, not man nor beast, would want to be subjected to an eternal, infernal scream even if it were to end within days as the fleet moved further away after consuming what it could. Noise and heat are the only real pollutants of this system; taking noise seriously from the beginning is paramount.
Fire Safety
A “fire-breathing dragon” is not the worst description of the Forest Walker. It eats wood, combusts it at very high temperatures and excretes carbon; and it does so in an extremely flammable environment. Bad mix for one Forest Walker, worse for many. One must take extreme pains to ensure that during normal operation, a Forest Walker could fall over, walk through tinder dry brush, or get pounded into the ground by a meteorite from Krypton and it wouldn’t destroy epic swaths of trees and baby deer. I envision an ultimate test of a prototype to include dowsing it in grain alcohol while it’s wrapped up in toilet paper like a pledge at a fraternity party. If it runs for 72 hours and doesn’t set everything on fire, then maybe outside entities won’t be fearful of something that walks around forests with a constant fire in its belly.
The Wrap
How we think about what can be done with and adjacent to Bitcoin is at least as important as Bitcoin’s economic standing itself. For those who will tell me that this entire idea is without merit, I say, “OK, fine. You can come up with something, too.” What can we plug Bitcoin into that, like a battery, makes something that does not work, work? That’s the lesson I get from this entire exercise. No one was ever going to hire teams of humans to go out and "clean the forest". There's no money in that. The data collection and sales from such an endeavor might provide revenues over the break-even point but investment demands Alpha in this day and age. But, plug Bitcoin into an almost viable system and, voilà! We tip the scales to achieve lift-off.
Let’s face it, we haven’t scratched the surface of Bitcoin’s forcing function on our minds. Not because it’s Bitcoin, but because of what that invention means. The question that pushes me to approach things this way is, “what can we create that one system’s waste is another system’s feedstock?” The Forest Walker system’s only real waste is the conversion of low entropy energy (wood and syngas) into high entropy energy (heat and noise). All other output is beneficial to humanity.
Bitcoin, I believe, is the first product of a new mode of human imagination. An imagination newly forged over the past few millennia of being lied to, stolen from, distracted and otherwise mis-allocated to a black hole of the nonsensical. We are waking up.
What I have presented is not science fiction. Everything I have described here is well within the realm of possibility. The question is one of viability, at least in terms of the detritus of the old world we find ourselves departing from. This system would take a non-trivial amount of time and resources to develop. I think the system would garner extensive long-term contracts from those who have the most to lose from wildfires, the most to gain from hyperaccurate data sets, and, of course, securing the most precious asset in the world. Many may not see it that way, for they seek Alpha and are therefore blind to other possibilities. Others will see only the possibilities; of thinking in a new way, of looking at things differently, and dreaming of what comes next.
-
 @ 86dfbe73:628cef55
2025-05-25 08:20:07
@ 86dfbe73:628cef55
2025-05-25 08:20:07Robustheit ist die Eigenschaft eines Systems, auch unter schwierigen Bedingungen funktionieren zu können: trotz Störungen und einer gewissen Verschlechterung seiner internen Prozesse. Das Leben als Ganzes ist robust. Dasselbe gilt für Ökosysteme: Sie können den Verlust einiger Arten überstehen und sich an veränderte Umweltbedingungen anpassen.
Der Hauptfeind der Robustheit ist das Streben nach Effizienz. Ein auf Effizienz optimiertes System hat keine Reserven mehr, sich an Störungen anzupassen. Es wird fragil. Wir optimieren die Gesellschaft und ihre Subsysteme (z. B. Institutionen) seit 5000 Jahren auf Wachstum, Effizienz und Produktivität. Und wir haben das Optimierungstempo mit den beiden Turbo-Boosts fossile Brennstoffe und Informationstechnologie beschleunigt. Deshalb ist alles um uns herum fragil geworden. Beispielsweise kann ein Virusausbruch in China sich zu einer Pandemie entwickeln, weil die Menschen weit und schnell reisen können und müssen.
Robustheit ist nicht absolut und dauerhaft. Ein System kann durch Störungen, die zu gravierend für es sind, fragil werden. Ehemals robuste Ökosysteme wie Regenwälder wurden durch menschliche Ausbeutung fragil. Deregulierung hat sowohl Regierungen als auch die Wirtschaft effizienter gemacht, allerdings zum Preis zunehmender Fragilität. Unternehmen sind mächtiger geworden als viele Staaten, was bedeutet, dass demokratisch gewählte Parlamente und Regierungen nicht mehr die Kontrolle haben. Heute kann eine einzelne Person demokratische Wahlen weltweit manipulieren, indem sie ein soziales Netzwerk kontrolliert. Das ist Fragilität pur.
Wir müssen als Gesellschaft die Effizienz in den Hintergrund rücken und uns mehr auf Robustheit konzentrieren.
-
 @ 000002de:c05780a7
2025-05-21 17:27:46
@ 000002de:c05780a7
2025-05-21 17:27:46I completely missed this until yesterday. I was listening to our local news talk station and it came up. They had some people that were pretty knowledgeable about prostate cancer on. They talked about other presidents being tested while in office for it. They came to conclusion that it is possible that Biden wasn't having his PSA checked. This is pretty normal for a old dude his age. But it is not normal for a President his age.
My thought is much simpler.
We know his doctors, the media, and his admin were lying about his health when he was in office. Hello! Anyone paying attention and not invested in his regime knew he was declining mentally in front of our very eyes. They covered for him over and over again. Only those that don't pay attention or discounted his critics completely was surprised by his debate performance.
To be clear though, Biden is far from the first president to do this. Wilson, FDR, Kennedy, and Reagan all had issues and they were kept from the public. If we learned these things in school we might actually have a public that thinks critically once and a while.
So, with that in mind do you really think the regime would not withhold medical info about this cancer? Come on. Don't be naive. He clearly was not in charge 100% of the time while in office and the regime wanted to maintain power. Sharing that he had prostate cancer would not be on the menu.
Politics is like a drug that numbs the brain. Because people don't like one party or person they retard their thinking. Its the same thing as happens in sports. Fans of one team see the same play completely differently from the other team's fans. Politics and the investment into parties kills most people's objectivity.
I don't trust liars. It honestly blows my mind how trusting people can be of professional liars. Both parties are full of liars. Trump is a liar and those opposing him are liars. We are drowning in lies. You can vote for a lessor of two evils but never forget what they are.
https://stacker.news/items/985791
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 8d34bd24:414be32b
2025-05-21 15:52:46
@ 8d34bd24:414be32b
2025-05-21 15:52:46In our culture today, people like to have “my truth” as opposed to “your truth.” They want to have teachers who tell them what they want to hear and worship in the way they desire. The Bible predicted these times.
For the time will come when people will not put up with sound doctrine. Instead, to suit their own desires, they will gather around them a great number of teachers to say what their itching ears want to hear. (2 Timothy 4:3)
My question is, “do we get to choose what we want to believe about God and how we want to worship Him, or does God tell us what we are to believe and how we are to worship Him?”
The Bible makes it clear that He is who He says He is and He expects obedience and worship according to His commands. We do not get to decide for ourselves.
The woman said to Him, “Sir, I perceive that You are a prophet. Our fathers worshiped in this mountain, and you people say that in Jerusalem is the place where men ought to worship.” Jesus said to her, “Woman, believe Me, an hour is coming when neither in this mountain nor in Jerusalem will you worship the Father. You worship what you do not know; we worship what we know, for salvation is from the Jews. But an hour is coming, and now is, when the true worshipers will worship the Father in spirit and truth; for such people the Father seeks to be His worshipers. God is spirit, and those who worship Him must worship in spirit and truth.” (John 4:19-24) {emphasis mine}
In this passage, Jesus gently corrects the woman for worshipping what she does not know. He also says, “God is spirit, and those who worship Him must worship in spirit and truth.” He states what God is (spirit) and how He must be worshipped “in spirit and truth.” We don’t get to define God however we wish, and we don’t get to worship Him any way we wish. God is who He has revealed Himself to be and we must obey Him and worship Him the way He has commanded.
In this next passage, God makes clear that He is holy and we do not get to worship Him any way we wish. We are to interact with Him in the prescribed manner.
Now Nadab and Abihu, the sons of Aaron, took their respective firepans, and after putting fire in them, placed incense on it and offered strange fire before the Lord, which He had not commanded them. And fire came out from the presence of the Lord and consumed them, and they died before the Lord. Then Moses said to Aaron, “It is what the Lord spoke, saying,
‘By those who come near Me I will be treated as holy,\ And before all the people I will be honored.’ ”
So Aaron, therefore, kept silent. (Leviticus 10:1-3) {emphasis mine}
God had prescribed a particular way to approach Him and only those whom He had chosen (priests of the lineage of Aaron). Nadab and Abihu chose to “do it their way” and paid the price for ignoring God’s command. God set an example with them.
God has been gracious enough to reveal Himself, His character, His power, and His commands to us. If we have truly submitted ourselves to His rule, we should hunger for God’s words so we can know Him better and honor Him in obedience.
But now I come to You; and these things I speak in the world so that they may have My joy made full in themselves. I have given them Your word; and the world has hated them, because they are not of the world, even as I am not of the world. I do not ask You to take them out of the world, but to keep them from the evil one. They are not of the world, even as I am not of the world. Sanctify them in the truth; Your word is truth. (John 17:13-17) {emphasis mine}
In today’s culture, everybody likes to claim their own personal truth, but that isn’t how truth works. The truth is not determined by an individual for themselves. It isn’t even determined by a consensus or majority vote. The truth is the truth even if not one person on earth believes it. God speaks truth and God is truth. Our belief or lack thereof doesn’t change the truth, but our lack of belief in the truth, especially the truth as revealed by God in His word, can negatively affect our relationship with God.
God expects us to study His word so we can obey His commands.
For I did not speak to your fathers, or command them in the day that I brought them out of the land of Egypt, concerning burnt offerings and sacrifices. But this is what I commanded them, saying, ‘Obey My voice, and I will be your God, and you will be My people; and you will walk in all the way which I command you, that it may be well with you.’ Yet they did not obey or incline their ear, but walked in their own counsels and in the stubbornness of their evil heart, and went backward and not forward. Since the day that your fathers came out of the land of Egypt until this day, I have sent you all My servants the prophets, daily rising early and sending them. Yet they did not listen to Me or incline their ear, but stiffened their neck; they did more evil than their fathers. (Jeremiah 7:22-26) {emphasis mine}
Today you rarely see someone bowing down to a golden idol, but that doesn’t mean that we are any better at obeying God’s commands or submitting to His will. We still try to make God in our own image so He is a convenience to us and how we want to live our lives. We still put other things ahead of God — family, work, entertainment, fame, etc. Most of us aren’t any more faithful to God than the Israelites were. Just like the Israelites, we put on the trappings of faith but don’t live according to faith and faithfulness.
And He said to them, “Rightly did Isaiah prophesy of you hypocrites, as it is written:
‘This people honors Me with their lips,\ But their heart is far away from Me.\ **But in vain do they worship Me,\ Teaching as doctrines the precepts of men.’\ Neglecting the commandment of God, you hold to the tradition of men.”
He was also saying to them, “You are experts at setting aside the commandment of God in order to keep your tradition. (Mark 7:6-9) {emphasis mine}
How many “churches” and “Christian” leaders teach people according to the culture instead of according to the Word of God? How many tell people what they want to hear and what makes them feel good instead of what they need to hear — the truth as spoken through the Bible? How many church attenders follow a “Christian” leader more than they follow their Creator, Savior, and God? How many church attenders can recite the words of their leaders better than the Holy Scriptures?
I solemnly charge you in the presence of God and of Christ Jesus, who is to judge the living and the dead, and by His appearing and His kingdom: preach the word; be ready in season and out of season; reprove, rebuke, exhort, with great patience and instruction. For the time will come when they will not endure sound doctrine; but wanting to have their ears tickled, they will accumulate for themselves teachers in accordance to their own desires, and will turn away their ears from the truth and will turn aside to myths. But you, be sober in all things, endure hardship, do the work of an evangelist, fulfill your ministry. (2 Timothy 4:1-5) {emphasis mine}
How can we know if a church leader is rightly preaching God’s word? We can only know if we have read the Bible and studied it. We should be like the Bereans:
Now these were more noble-minded than those in Thessalonica, for they received the word with great eagerness, examining the Scriptures daily to see whether these things were so. (Acts 17:11)
Honestly, I don’t trust any spiritual leader who doesn’t encourage me to search the Scriptures to see whether their words are true. Any leader who puts their own word above the Scriptures is a false teacher. Sadly there are many, maybe more than faithful teachers. Some false teachers are intentionally so, but many have been misled by other false teachers. Their guilt is less, but they don’t do any less harm than those who intentionally mislead.
We need to seek trustworthy teachers who speak according to the Word of God, who quote the Bible to support their opinions, and who seek the good of their followers rather than the submission of their followers.
Do not harden your hearts, as at Meribah,\ As in the day of Massah in the wilderness,
“When your fathers tested Me,\ They tried Me, though they had seen My work.\ For forty years I loathed that generation,\ And said they are a people who err in their heart,\ And they do not know My ways.\ Therefore I swore in My anger,\ Truly they shall not enter into My rest.” (Psalm 95:8-11) {emphasis mine} *Teach me good discernment and knowledge,\ For I believe in Your commandments*.\ Before I was afflicted I went astray,\ But now I keep Your word.\ You are good and do good;\ Teach me Your statutes.\ The arrogant have forged a lie against me;\ *With all my heart I will observe Your precepts*.\ Their heart is covered with fat,\ But I delight in Your law.\ It is good for me that I was afflicted,\ That I may learn Your statutes.\ The law of Your mouth is better to me\ Than thousands of gold and silver pieces. (Psalm 119:66-72) {emphasis mine}
May our Creator God teach us the truth. May He fill our hearts with the desire to be in His word daily and to seek His will. May He do what is necessary to get our attention and turn our hearts and minds fully to Him, so we can learn His statutes and serve Him faithfully, so one day we are blessed to hear, “Well done! Good and faithful servant.”
Trust Jesus.
FYI, I see lack of knowledge of truth and God’s word as one of the biggest problems in the church today; however, it is possible to know the Bible in depth, but not know God. As important as knowledge of Scriptures is, this knowledge (without faith, submission, obedience, and love) is meaningless. Knowledge doesn’t get us to heaven. Even obedience doesn’t get us to heaven. Only faith and submission to our creator God leads to salvation and heaven. That being said, we can’t faithfully serve our God without knowledge of Him and His commands. Out of gratefulness for who He is and what He has done for us, we should seek to know and please Him.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 57d1a264:69f1fee1
2025-05-25 06:26:42
@ 57d1a264:69f1fee1
2025-05-25 06:26:42I dare to claim that the big factor is the absence of an infinite feed design.
Modern social media landscape sucks for a myriad of reasons, but oh boy does the infinite feed take the crapcake. It's not just bad on it's own, it's emblematic of most, if not all other ways social media have deteriorated into an enshitification spiral. Let's see at just three things I hate about it the most.
1) It's addictive: In the race for your attention, every addictive design element helps. But infinite feed is addictive almost by default. Users are expected to pull the figurative lever until they hit a jackpot. Just one more reel, then I'll go to sleep.
2) Autonomy? What's that? You are not the one driving your experience. No. You are just a passenger passively absorbing what the feed feeds you.
3) Echo chambers. The algorithm might be more to blame here, but the infinite feed and it's super-limited exploration options sure don't help. Your feed only goes two ways - into the past and into the comfortable.
And I could go on, and on...
The point it, if the goal of every big tech company is to have us mindlessly and helplessly consume their products, without agency and opposition (and it is $$$), then the infinite feed gets them half-way there.
Let's get rid of it. For the sake of humanity.
Aphantasia [^1]
Version: 1.0.2 AlphaWhat is Aphantasia?
I like to call it a social network for graph enthusiasts. It's a place where your thoughts live in time and space, interconnected with others and explorable in a graph view.
The code is open-source and you can take a look at it on GitHub. There you can find more information about contributions, API usage and other details related to the software.
There is also an accompanying youtube channel.
https://www.youtube.com/watch?v=JeLOt-45rJM
[^1]: Aphantasia the software is named after aphantasia the condition - see Wikipedia for more information.
https://stacker.news/items/988754
-
 @ e3ba5e1a:5e433365
2025-01-13 16:47:27
@ e3ba5e1a:5e433365
2025-01-13 16:47:27My blog posts and reading material have both been on a decidedly economics-heavy slant recently. The topic today, incentives, squarely falls into the category of economics. However, when I say economics, I’m not talking about “analyzing supply and demand curves.” I’m talking about the true basis of economics: understanding how human beings make decisions in a world of scarcity.
A fair definition of incentive is “a reward or punishment that motivates behavior to achieve a desired outcome.” When most people think about economic incentives, they’re thinking of money. If I offer my son $5 if he washes the dishes, I’m incentivizing certain behavior. We can’t guarantee that he’ll do what I want him to do, but we can agree that the incentive structure itself will guide and ultimately determine what outcome will occur.
The great thing about monetary incentives is how easy they are to talk about and compare. “Would I rather make $5 washing the dishes or $10 cleaning the gutters?” But much of the world is incentivized in non-monetary ways too. For example, using the “punishment” half of the definition above, I might threaten my son with losing Nintendo Switch access if he doesn’t wash the dishes. No money is involved, but I’m still incentivizing behavior.
And there are plenty of incentives beyond our direct control! My son is also incentivized to not wash dishes because it’s boring, or because he has some friends over that he wants to hang out with, or dozens of other things. Ultimately, the conflicting array of different incentive structures placed on him will ultimately determine what actions he chooses to take.
Why incentives matter
A phrase I see often in discussions—whether they are political, parenting, economic, or business—is “if they could just do…” Each time I see that phrase, I cringe a bit internally. Usually, the underlying assumption of the statement is “if people would behave contrary to their incentivized behavior then things would be better.” For example:
- If my kids would just go to bed when I tell them, they wouldn’t be so cranky in the morning.
- If people would just use the recycling bin, we wouldn’t have such a landfill problem.
- If people would just stop being lazy, our team would deliver our project on time.
In all these cases, the speakers are seemingly flummoxed as to why the people in question don’t behave more rationally. The problem is: each group is behaving perfectly rationally.
- The kids have a high time preference, and care more about the joy of staying up now than the crankiness in the morning. Plus, they don’t really suffer the consequences of morning crankiness, their parents do.
- No individual suffers much from their individual contribution to a landfill. If they stopped growing the size of the landfill, it would make an insignificant difference versus the amount of effort they need to engage in to properly recycle.
- If a team doesn’t properly account for the productivity of individuals on a project, each individual receives less harm from their own inaction. Sure, the project may be delayed, company revenue may be down, and they may even risk losing their job when the company goes out of business. But their laziness individually won’t determine the entirety of that outcome. By contrast, they greatly benefit from being lazy by getting to relax at work, go on social media, read a book, or do whatever else they do when they’re supposed to be working.

My point here is that, as long as you ignore the reality of how incentives drive human behavior, you’ll fail at getting the outcomes you want.
If everything I wrote up until now made perfect sense, you understand the premise of this blog post. The rest of it will focus on a bunch of real-world examples to hammer home the point, and demonstrate how versatile this mental model is.
Running a company
Let’s say I run my own company, with myself as the only employee. My personal revenue will be 100% determined by my own actions. If I decide to take Tuesday afternoon off and go fishing, I’ve chosen to lose that afternoon’s revenue. Implicitly, I’ve decided that the enjoyment I get from an afternoon of fishing is greater than the potential revenue. You may think I’m being lazy, but it’s my decision to make. In this situation, the incentive–money–is perfectly aligned with my actions.
Compare this to a typical company/employee relationship. I might have a bank of Paid Time Off (PTO) days, in which case once again my incentives are relatively aligned. I know that I can take off 15 days throughout the year, and I’ve chosen to use half a day for the fishing trip. All is still good.
What about unlimited time off? Suddenly incentives are starting to misalign. I don’t directly pay a price for not showing up to work on Tuesday. Or Wednesday as well, for that matter. I might ultimately be fired for not doing my job, but that will take longer to work its way through the system than simply not making any money for the day taken off.
Compensation overall falls into this misaligned incentive structure. Let’s forget about taking time off. Instead, I work full time on a software project I’m assigned. But instead of using the normal toolchain we’re all used to at work, I play around with a new programming language. I get the fun and joy of playing with new technology, and potentially get to pad my resume a bit when I’m ready to look for a new job. But my current company gets slower results, less productivity, and is forced to subsidize my extracurricular learning.
When a CEO has a bonus structure based on profitability, he’ll do everything he can to make the company profitable. This might include things that actually benefit the company, like improving product quality, reducing internal red tape, or finding cheaper vendors. But it might also include destructive practices, like slashing the R\&D budget to show massive profits this year, in exchange for a catastrophe next year when the next version of the product fails to ship.

Or my favorite example. My parents owned a business when I was growing up. They had a back office where they ran operations like accounting. All of the furniture was old couches from our house. After all, any money they spent on furniture came right out of their paychecks! But in a large corporate environment, each department is generally given a budget for office furniture, a budget which doesn’t roll over year-to-year. The result? Executives make sure to spend the entire budget each year, often buying furniture far more expensive than they would choose if it was their own money.
There are plenty of details you can quibble with above. It’s in a company’s best interest to give people downtime so that they can come back recharged. Having good ergonomic furniture can in fact increase productivity in excess of the money spent on it. But overall, the picture is pretty clear: in large corporate structures, you’re guaranteed to have mismatches between the company’s goals and the incentive structure placed on individuals.
Using our model from above, we can lament how lazy, greedy, and unethical the employees are for doing what they’re incentivized to do instead of what’s right. But that’s simply ignoring the reality of human nature.
Moral hazard
Moral hazard is a situation where one party is incentivized to take on more risk because another party will bear the consequences. Suppose I tell my son when he turns 21 (or whatever legal gambling age is) that I’ll cover all his losses for a day at the casino, but he gets to keep all the winnings.
What do you think he’s going to do? The most logical course of action is to place the largest possible bets for as long as possible, asking me to cover each time he loses, and taking money off the table and into his bank account each time he wins.

But let’s look at a slightly more nuanced example. I go to a bathroom in the mall. As I’m leaving, I wash my hands. It will take me an extra 1 second to turn off the water when I’m done washing. That’s a trivial price to pay. If I don’t turn off the water, the mall will have to pay for many liters of wasted water, benefiting no one. But I won’t suffer any consequences at all.
This is also a moral hazard, but most people will still turn off the water. Why? Usually due to some combination of other reasons such as:
- We’re so habituated to turning off the water that we don’t even consider not turning it off. Put differently, the mental effort needed to not turn off the water is more expensive than the 1 second of time to turn it off.
- Many of us have been brought up with a deep guilt about wasting resources like water. We have an internal incentive structure that makes the 1 second to turn off the water much less costly than the mental anguish of the waste we created.
- We’re afraid we’ll be caught by someone else and face some kind of social repercussions. (Or maybe more than social. Are you sure there isn’t a law against leaving the water tap on?)
Even with all that in place, you may notice that many public bathrooms use automatic water dispensers. Sure, there’s a sanitation reason for that, but it’s also to avoid this moral hazard.
A common denominator in both of these is that the person taking the action that causes the liability (either the gambling or leaving the water on) is not the person who bears the responsibility for that liability (the father or the mall owner). Generally speaking, the closer together the person making the decision and the person incurring the liability are, the smaller the moral hazard.
It’s easy to demonstrate that by extending the casino example a bit. I said it was the father who was covering the losses of the gambler. Many children (though not all) would want to avoid totally bankrupting their parents, or at least financially hurting them. Instead, imagine that someone from the IRS shows up at your door, hands you a credit card, and tells you you can use it at a casino all day, taking home all the chips you want. The money is coming from the government. How many people would put any restriction on how much they spend?
And since we’re talking about the government already…
Government moral hazards
As I was preparing to write this blog post, the California wildfires hit. The discussions around those wildfires gave a huge number of examples of moral hazards. I decided to cherry-pick a few for this post.
The first and most obvious one: California is asking for disaster relief funds from the federal government. That sounds wonderful. These fires were a natural disaster, so why shouldn’t the federal government pitch in and help take care of people?
The problem is, once again, a moral hazard. In the case of the wildfires, California and Los Angeles both had ample actions they could have taken to mitigate the destruction of this fire: better forest management, larger fire department, keeping the water reservoirs filled, and probably much more that hasn’t come to light yet.
If the federal government bails out California, it will be a clear message for the future: your mistakes will be fixed by others. You know what kind of behavior that incentivizes? More risky behavior! Why spend state funds on forest management and extra firefighters—activities that don’t win politicians a lot of votes in general—when you could instead spend it on a football stadium, higher unemployment payments, or anything else, and then let the feds cover the cost of screw-ups.
You may notice that this is virtually identical to the 2008 “too big to fail” bail-outs. Wall Street took insanely risky behavior, reaped huge profits for years, and when they eventually got caught with their pants down, the rest of us bailed them out. “Privatizing profits, socializing losses.”

And here’s the absolute best part of this: I can’t even truly blame either California or Wall Street. (I mean, I do blame them, I think their behavior is reprehensible, but you’ll see what I mean.) In a world where the rules of the game implicitly include the bail-out mentality, you would be harming your citizens/shareholders/investors if you didn’t engage in that risky behavior. Since everyone is on the hook for those socialized losses, your best bet is to maximize those privatized profits.
There’s a lot more to government and moral hazard, but I think these two cases demonstrate the crux pretty solidly. But let’s leave moral hazard behind for a bit and get to general incentivization discussions.
Non-monetary competition
At least 50% of the economics knowledge I have comes from the very first econ course I took in college. That professor was amazing, and had some very colorful stories. I can’t vouch for the veracity of the two I’m about to share, but they definitely drive the point home.
In the 1970s, the US had an oil shortage. To “fix” this problem, they instituted price caps on gasoline, which of course resulted in insufficient gasoline. To “fix” this problem, they instituted policies where, depending on your license plate number, you could only fill up gas on certain days of the week. (Irrelevant detail for our point here, but this just resulted in people filling up their tanks more often, no reduction in gas usage.)
Anyway, my professor’s wife had a friend. My professor described in great detail how attractive this woman was. I’ll skip those details here since this is a PG-rated blog. In any event, she never had any trouble filling up her gas tank any day of the week. She would drive up, be told she couldn’t fill up gas today, bat her eyes at the attendant, explain how helpless she was, and was always allowed to fill up gas.
This is a demonstration of non-monetary compensation. Most of the time in a free market, capitalist economy, people are compensated through money. When price caps come into play, there’s a limit to how much monetary compensation someone can receive. And in that case, people find other ways of competing. Like this woman’s case: through using flirtatious behavior to compensate the gas station workers to let her cheat the rules.
The other example was much more insidious. Santa Monica had a problem: it was predominantly wealthy and white. They wanted to fix this problem, and decided to put in place rent controls. After some time, they discovered that Santa Monica had become wealthier and whiter, the exact opposite of their desired outcome. Why would that happen?
Someone investigated, and ended up interviewing a landlady that demonstrated the reason. She was an older white woman, and admittedly racist. Prior to the rent controls, she would list her apartments in the newspaper, and would be legally obligated to rent to anyone who could afford it. Once rent controls were in place, she took a different tact. She knew that she would only get a certain amount for the apartment, and that the demand for apartments was higher than the supply. That meant she could be picky.
She ended up finding tenants through friends-of-friends. Since it wasn’t an official advertisement, she wasn’t legally required to rent it out if someone could afford to pay. Instead, she got to interview people individually and then make them an offer. Normally, that would have resulted in receiving a lower rental price, but not under rent controls.
So who did she choose? A young, unmarried, wealthy, white woman. It made perfect sense. Women were less intimidating and more likely to maintain the apartment better. Wealthy people, she determined, would be better tenants. (I have no idea if this is true in practice or not, I’m not a landlord myself.) Unmarried, because no kids running around meant less damage to the property. And, of course, white. Because she was racist, and her incentive structure made her prefer whites.
You can deride her for being racist, I won’t disagree with you. But it’s simply the reality. Under the non-rent-control scenario, her profit motive for money outweighed her racism motive. But under rent control, the monetary competition was removed, and she was free to play into her racist tendencies without facing any negative consequences.
Bureaucracy
These were the two examples I remember for that course. But non-monetary compensation pops up in many more places. One highly pertinent example is bureaucracies. Imagine you have a government office, or a large corporation’s acquisition department, or the team that apportions grants at a university. In all these cases, you have a group of people making decisions about handing out money that has no monetary impact on them. If they give to the best qualified recipients, they receive no raises. If they spend the money recklessly on frivolous projects, they face no consequences.
Under such an incentivization scheme, there’s little to encourage the bureaucrats to make intelligent funding decisions. Instead, they’ll be incentivized to spend the money where they recognize non-monetary benefits. This is why it’s so common to hear about expensive meals, gift bags at conferences, and even more inappropriate ways of trying to curry favor with those that hold the purse strings.
Compare that ever so briefly with the purchases made by a small mom-and-pop store like my parents owned. Could my dad take a bribe to buy from a vendor who’s ripping him off? Absolutely he could! But he’d lose more on the deal than he’d make on the bribe, since he’s directly incentivized by the deal itself. It would make much more sense for him to go with the better vendor, save $5,000 on the deal, and then treat himself to a lavish $400 meal to celebrate.
Government incentivized behavior
This post is getting longer in the tooth than I’d intended, so I’ll finish off with this section and make it a bit briefer. Beyond all the methods mentioned above, government has another mechanism for modifying behavior: through directly changing incentives via legislation, regulation, and monetary policy. Let’s see some examples:
- Artificial modification of interest rates encourages people to take on more debt than they would in a free capital market, leading to malinvestment and a consumer debt crisis, and causing the boom-bust cycle we all painfully experience.
- Going along with that, giving tax breaks on interest payments further artificially incentivizes people to take on debt that they wouldn’t otherwise.
- During COVID-19, at some points unemployment benefits were greater than minimum wage, incentivizing people to rather stay home and not work than get a job, leading to reduced overall productivity in the economy and more printed dollars for benefits. In other words, it was a perfect recipe for inflation.
- The tax code gives deductions to “help” people. That might be true, but the real impact is incentivizing people to make decisions they wouldn’t have otherwise. For example, giving out tax deductions on children encourages having more kids. Tax deductions on childcare and preschools incentivizes dual-income households. Whether or not you like the outcomes, it’s clear that it’s government that’s encouraging these outcomes to happen.
- Tax incentives cause people to engage in behavior they wouldn’t otherwise (daycare+working mother, for example).
- Inflation means that the value of your money goes down over time, which encourages people to spend more today, when their money has a larger impact. (Milton Friedman described this as high living.)
Conclusion
The idea here is simple, and fully encapsulated in the title: incentives determine outcomes. If you want to know how to get a certain outcome from others, incentivize them to want that to happen. If you want to understand why people act in seemingly irrational ways, check their incentives. If you’re confused why leaders (and especially politicians) seem to engage in destructive behavior, check their incentives.
We can bemoan these realities all we want, but they are realities. While there are some people who have a solid internal moral and ethical code, and that internal code incentivizes them to behave against their externally-incentivized interests, those people are rare. And frankly, those people are self-defeating. People should take advantage of the incentives around them. Because if they don’t, someone else will.
(If you want a literary example of that last comment, see the horse in Animal Farm.)
How do we improve the world under these conditions? Make sure the incentives align well with the overall goals of society. To me, it’s a simple formula:
- Focus on free trade, value for value, as the basis of a society. In that system, people are always incentivized to provide value to other people.
- Reduce the size of bureaucracies and large groups of all kinds. The larger an organization becomes, the farther the consequences of decisions are from those who make them.
- And since the nature of human beings will be to try and create areas where they can control the incentive systems to their own benefits, make that as difficult as possible. That comes in the form of strict limits on government power, for example.
And even if you don’t want to buy in to this conclusion, I hope the rest of the content was educational, and maybe a bit entertaining!
-
 @ 502ab02a:a2860397
2025-05-25 01:03:51
@ 502ab02a:a2860397
2025-05-25 01:03:51บางครั้งพลังยิ่งใหญ่ที่สุดก็ไม่ใช่สิ่งที่เห็นได้ด้วยตาเปล่า เหมือนแสงแดดที่คนส่วนใหญ่มักจะกลัวเพราะกลัวผิวเสีย กลัวฝ้า กลัวร้อน แต่แท้จริงแล้วในแสงแดดมีบางสิ่งที่น่าเคารพอยู่ลึกๆ มันคือแสงที่มองไม่เห็น มันไม่แสบตา ไม่แสบผิว แต่มันลึก ถึงเซลล์ มันคือ “แสงอินฟราเรด” ที่ซ่อนตัวอย่างสุภาพในแดดยามเช้า
เฮียมักชอบพูดว่า แดดที่ดีไม่จำเป็นต้องแสบหลัง อาบแสงที่ลอดผ่านใบไม้ยามเช้าแบบไม่ต้องฝืนตาก็พอ แสงอินฟราเรดนี่แหละคือพระเอกตัวจริงในความเงียบ มันไม่ดัง ไม่โชว์ ไม่โฆษณา แต่มันลงลึกไปถึงระดับที่ร่างกายเรากำลังหิวโดยไม่รู้ตัวในระดับเซลล์
ในเซลล์ของเรา มีหน่วยผลิตพลังงานที่เรียกว่าไมโทคอนเดรีย เจ้านี่แหละคือโรงไฟฟ้าจิ๋วประจำบ้าน ที่ต้องตื่นมาทำงานทุกวันโดยไม่ได้หยุดเสาร์อาทิตย์ ยิ่งถ้าไมโทคอนเดรียทำงานไม่ดี ร่างกายก็จะเหมือนไฟตกทั้งระบบ—ง่วงง่าย เพลียไว ปวดนู่นปวดนี่เหมือนไฟในบ้านกระพริบตลอดเวลา
แล้วแสงอินฟราเรดเกี่ยวอะไรกับมัน? เฮียขอเล่าง่ายๆ ว่า ไมโทคอนเดรียมีตัวรับแสงตัวหนึ่งชื่อว่า cytochrome c oxidase เจ้านี่ตอบสนองต่อแสงอินฟราเรดช่วงคลื่นเฉพาะ คือประมาณ 600–900 นาโนเมตร พอโดนเข้าไป มันเหมือนได้จุดประกายให้โรงงานพลังงานในร่างกายกลับมาคึกคักอีกครั้ง ผลิตพลังงานได้มากขึ้น ระบบไหลเวียนเลือดก็ดีขึ้น เหมือนท่อน้ำที่เคยอุดตันก็กลับมาใสแจ๋ว ความอักเสบเล็กๆ ในร่างกายก็ลดลง คล้ายบ้านที่เคยอับชื้นแล้วได้เปิดหน้าต่างให้แสงแดดส่องเข้าไป
และที่น่ารักกว่านั้นคือ เราไม่ต้องไปถึงชายหาด ไม่ต้องจองรีสอร์ตริมทะเล แค่แดดเช้าอ่อนๆ ข้างบ้านหรือตามขอบระเบียง ก็ให้แสงอินฟราเรดได้แล้ว ถ้าใครอยู่ในเมืองใหญ่ที่มีแต่ตึกบังแดด แล้วจะเลือกใช้หลอดไฟ Red Light Therapy ก็ไม่ผิด แต่ต้องเลือกแบบรู้เท่าทันรู้ ไม่ใช่เห็นใครรีวิวก็ซื้อมาเปิดใส่หน้า หวังจะหน้าใสข้ามคืน ต้องเข้าใจทั้งความยาวคลื่น เวลาใช้งาน และจุดประสงค์ ไม่ใช่ใช้เพราะแค่กลัวแก่อยากหน้าตึง แต่ใช้เพราะอยากให้ร่างกายกลับไปทำงานอย่างเป็นธรรมชาติอีกครั้ง และอยู่ในประเทศหรือสถานที่ที่โดนแดดได้น้อยอยากได้เสริมเฉยๆ
แล้วเราจะรู้ได้ยังไงว่าไมโทคอนเดรียเรากลับมาทำงานดีขึ้น? เฮียว่าไม่ต้องรอผลเลือดจากแล็บไหนก็รู้ได้ อย่าไปยึดติดกับตัวเลขมากครับ เอาตัวเองเป็นหลัก ตั้งคำถามกับตัวเองว่ารู้สึกยังไงบ้าง ถ้าเริ่มนอนหลับลึกขึ้น ตื่นมาแล้วหัวไม่มึน ไม่หงุดหงิดตั้งแต่ยังไม่ลืมตา ถ้าปวดหลังปวดข้อที่เคยมีเริ่มหายไปแบบไม่ได้กินยา หรือแม้แต่ผิวที่ดูสดใสขึ้นแบบไม่ต้องง้อสกินแคร์ นั่นแหละคือเสียงขอบคุณเบาๆ จากไมโทคอนเดรียที่ได้แสงแดดแล้วกลับมามีชีวิตอีกครั้ง ถ้ามันดีก็คือดี
บางที เราไม่ต้องกินวิตามินเม็ดไหนเพิ่ม แค่เดินออกไปรับแดดเบาๆ ในเวลาเช้าๆ แล้วให้ร่างกายได้พูดคุยกับธรรมชาติบ้าง เพราะในความอบอุ่นเงียบๆ ของแสงอินฟราเรดนั้น มีเสียงเบาๆ ที่กำลังปลุกพลังในตัวเราให้กลับมาอีกครั้ง
แดดไม่ใช่ศัตรู ถ้าเรารู้จักมันในมุมที่ถูกต้อง เฮียแค่อยากชวนให้ลองเปลี่ยนจากคำว่า “กลัวแดด” เป็น “ฟังแดด” เพราะบางครั้งธรรมชาติไม่ได้พูดด้วยคำ แต่สื่อสารด้วยแสงที่แทรกผ่านหัวใจเราโดยไม่ต้องผ่านล่าม
บางคนอาจคิดในใจ “แหมเฮีย ก็ดีหรอก ถ้าได้ตื่นเช้า” 555555
เฮียเข้าใจดีเลยว่าไม่ใช่ทุกคนจะตื่นมาทันแดดยามเช้าได้เสมอไป ชีวิตคนเรามันไม่ได้เริ่มต้นพร้อมไก่ขันทุกวัน บางคนเพิ่งเข้านอนตอนตีสาม ตื่นอีกทีแดดก็แตะบ่ายเข้าไปแล้ว ไม่ต้องกังวลไปจ้ะ เพราะความมหัศจรรย์ของแสงอินฟราเรดยังมีให้เราได้ใช้แม้ในแดดยามเย็น
แดดช่วงเย็น โดยเฉพาะหลังสี่โมงเย็นไปจนเกือบหกโมง (หรือเร็วช้าตามฤดู) ก็ยังอุดมไปด้วยแสงอินฟราเรดในช่วงคลื่นที่ไมโทคอนเดรียชอบ แถมยังไม่มีรังสี UV ที่แรงจัดมารบกวนเหมือนตอนเที่ยง เรียกว่าเป็นแดดแบบละมุนๆ สำหรับคนที่อยาก “บำบัดใจ” แบบไม่ต้องร้อนจนหัวเปียก
เฮียเคยลองตากแดดเย็นเดินไปในสวนสาธารณะ แล้วรู้สึกว่ามันเหมือนได้รีเซ็ตจิตใจหลังวันเหนื่อยๆ ไปในตัว ยิ่งพอรู้ว่าในช่วงเวลานี้แสงที่ได้กำลังช่วยปลุกพลังงานในร่างกายแบบเงียบๆ ด้วยแล้ว มันทำให้เฮียยิ่งเคารพธรรมชาติมากขึ้นไปอีก เคยเห็นคนที่วันๆมีแต่ความเครียด ความโกรธ ความอาฆาตต่อโลกไหมหละ บางคนแค่โดนแดด แต่ไม่ได้ตากแดด การตากแดดคือปล่อยใจไปกับธรรมชาติ พูดคุยกับร่างกาย บอกเขาว่าเราจะทำตัวให้เป็นประโยชน์กับโลกใบนี้ ให้สมกับที่ใช้พลังงานของโลก
จะเช้าหรือเย็น สำคัญไม่เท่ากับความตั้งใจ เฮียว่าไม่ว่าชีวิตจะตื่นตอนไหน ถ้าเราให้เวลาแค่ 10–15 นาทีในแต่ละวัน ออกไปยืนให้แดดแตะหน้า แตะแขน หรือแค่ให้แสงลอดผ่านตาเบาๆ โดยไม่ต้องจ้องจ้าๆ ก็พอ แค่นี้ก็เป็นการให้ไมโทคอนเดรียได้หายใจ ได้ออกกำลังกายแบบของมัน และได้ส่งพลังกลับมาหาเราทั้งร่างกายและจิตใจ
สุดท้ายแล้ว แดดไม่ได้แบ่งชนชั้น ไม่เลือกว่าจะรักเฉพาะคนตื่นเช้า หรือโกรธคนตื่นสาย ขอแค่เรารู้จักเวลาและวิธีอยู่กับมันอย่างถูกจังหวะ แดดก็พร้อมจะให้เสมอ
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr #SundaySpecialเราจะไปเป็นหมูแดดเดียว
-
 @ ecda4328:1278f072
2025-05-21 11:44:17
@ ecda4328:1278f072
2025-05-21 11:44:17An honest response to objections — and an answer to the most important question: why does any of this matter?
Last updated: May 21, 2025\ \ 📄 Document version:\ EN: https://drive.proton.me/urls/A4A8Y8A0RR#Sj2OBsBYJFr1\ RU: https://drive.proton.me/urls/GS9AS1NB30#ZdKKb5ackB5e
\ Statement: Deflation is not the enemy, but a natural state in an age of technological progress.\ Criticism: in real macroeconomics, long-term deflation is linked to depressions.\ Deflation discourages borrowers and investors, and makes debt heavier.\ Natural ≠ Safe.
1. “Deflation → Depression, Debt → Heavier”
This is true in a debt-based system. Yes, in a fiat economy, debt balloons to the sky, and without inflation it collapses.
But Bitcoin offers not “deflation for its own sake,” but an environment where you don’t need to be in debt to survive. Where savings don’t melt away.\ Jeff Booth said it clearly:
“Technology is inherently deflationary. Fighting deflation with the printing press is fighting progress.”
You don’t have to take on credit to live in this system. Which means — deflation is not an enemy, but an ally.
💡 People often confuse two concepts:
-
That deflation doesn’t work in an economy built on credit and leverage — that’s true.
-
That deflation itself is bad — that’s a myth.
📉 In reality, deflation is the natural state of a free market when technology makes everything cheaper.
Historical example:\ In the U.S., from the Civil War to the early 1900s, the economy experienced gentle deflation — alongside economic growth, employment expansion, and industrial boom.\ Prices fell: for example, a sack of flour cost \~$1.00 in 1865 and \~$0.50 in 1895 — and there was no crisis, because wages held and productivity increased.
Modern example:\ Consumer electronics over the past 20–30 years are a vivid example of technological deflation:\ – What cost $5,000 in 2000 (e.g., a 720p plasma TV) now costs $300 and delivers 10× better quality.\ – Phones, computers, cameras — all became far more powerful and cheaper at the same time.\ That’s how tech-driven deflation works: you get more for less.
📌 Bitcoin doesn’t make the world deflationary. It just doesn’t fight against deflation, unlike the fiat model that fights to preserve its debt pyramid.\ It stops punishing savers and rewards long-term thinkers.
Even economists often confuse organic tech deflation with crisis-driven (debt) deflation.
\ \ Statement: We’ve never lived in a truly free market — central banks and issuance always existed.\ Criticism: ideological statement.\ A truly “free” market is utopian.\ Banks and monetary issuance emerged in response to crises.\ A market without arbiters is not always fair, especially under imperfect competition.
2. “The Free Market Is a Utopia”
Yes, “pure markets” are rare. But what we have today isn’t regulation — it’s centralized power in the hands of central banks and cartels.
Bitcoin offers rules without rulers. 21 million. No one can change the issuance. It’s not ideology — it’s code instead of trust. And it has worked for 15 years.
💬 People often say that banks and centralized issuance emerged as a response to crises — as if the market couldn’t manage on its own.\ But if a system needs to be “rescued” again and again through money printing… maybe the problem isn’t freedom, but the system itself?
📌 Crises don’t disprove the value of free markets. They only reveal how fragile a system becomes when the price of money is set not by the market, but by a boardroom vote.\ Bitcoin doesn’t magically eliminate crises — it removes the root cause: the ability to manipulate money in someone’s interest.
\ \ Statement: Inflation is an invisible tax, especially on the poor and working class.\ Criticism: partly true: inflation can reduce debt burden, boost employment.\ The state indexes social benefits. Under stable inflation, compensators can work. Under deflation, things might be worse (mass layoffs, defaults).
3. “Inflation Can Help”
Theoretically — yes. Textbooks say moderate inflation can reduce debt burdens and stimulate consumption and jobs.\ But in practice — it works as a stealth tax, especially on those without assets. The wealthy escape — into real estate, stocks, funds.\ But the poor and working class lose purchasing power because their money is held in cash — and cash devalues.
💬 As Lyn Alden says:
“When your money can’t hold value, you’re forced to become an investor — even if you just want to save and live.”
The state may index pensions or benefits — but always with a lag, and always less than actual price increases.\ If bread rises 15% and your payment increase is 5%, you got poorer, even if the number on paper went up.
💥 We live in an inflationary system of everything:\ – Inflationary money\ – Inflationary products\ – Inflationary content\ – And now even inflationary minds
🧠 This is more than just rising prices — it’s a degradation of reality perception. You’re always rushing, everything loses meaning.\ But when did the system start working against you?
📉 What went wrong after 1971?
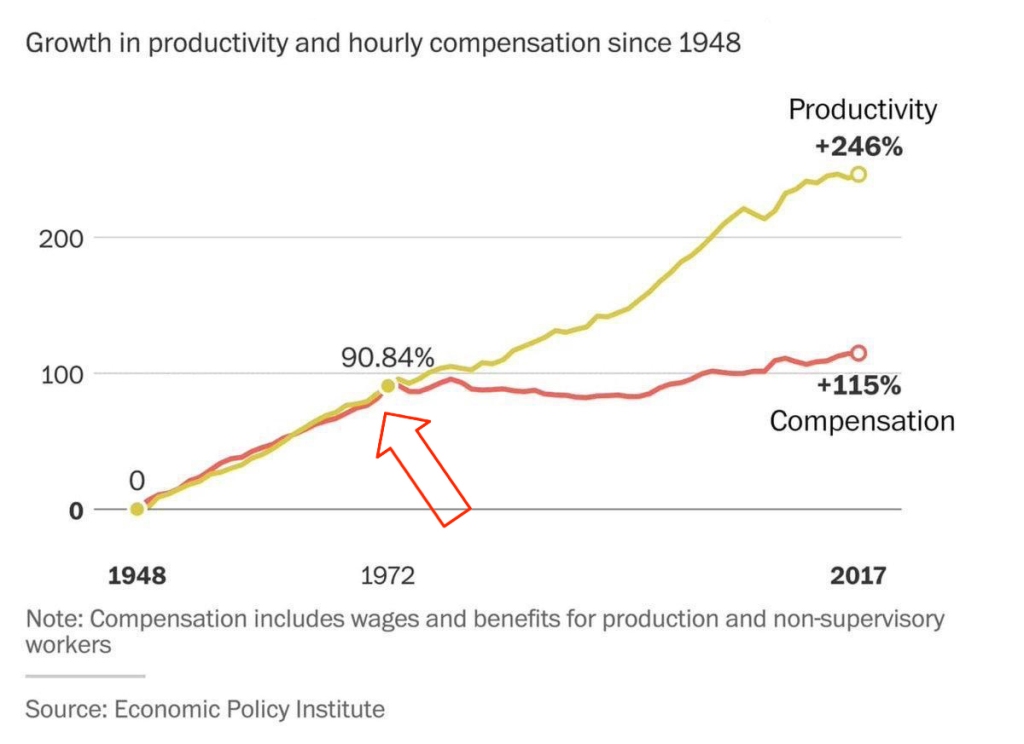 This chart shows that from 1948 to the early 1970s, productivity and wages grew together.\
But after the end of the gold standard in 1971 — the connection broke. Productivity kept rising, but real wages stalled.
This chart shows that from 1948 to the early 1970s, productivity and wages grew together.\
But after the end of the gold standard in 1971 — the connection broke. Productivity kept rising, but real wages stalled.👉 This means: you work more, better, faster — but buy less.
🔗 Source: wtfhappenedin1971.com
When you must spend today because tomorrow it’ll be worth less — that’s rewarding impulse and punishing long-term thinking.
Bitcoin offers a different environment:\ – Savings work\ – Long-term thinking is rewarded\ – The price of the future is calculated, not forced by a printing press
📌 Inflation can be a tool. But in government hands, it became a weapon — a slow, inevitable upward redistribution of wealth.
\ \ Statement: War is not growth, but a reallocation of resources into destruction.
Criticism: war can spur technological leaps (Internet, GPS, nuclear energy — all from military programs). "Military Keynesianism" was a real model.
4. “War Drives R&D”
Yes, wars sometimes give rise to tech spin-offs: Internet, GPS, nuclear power — all originated from military programs.
But that doesn’t make war a source of progress — it makes tech a byproduct of catastrophe.
“War reallocates resources toward destruction — not growth.”
Progress doesn’t happen because of war — it happens despite it.
If scientific breakthroughs require a million dead and burnt cities — maybe you’ve built your economy wrong.
💬 Even Michael Saylor said:
“If you need war to develop technology — you’ve built civilization wrong.”
No innovation justifies diverting human labor, minds, and resources toward destruction.\ War is always the opposite of efficiency — more is wasted than created.
🧠 Bitcoin, on the other hand, is an example of how real R&D happens without violence.\ No taxes. No army. Just math, voluntary participation, and open-source code.
📌 Military Keynesianism is not a model of progress — it’s a symptom of a sick monetary system that needs destruction to reboot.
Bitcoin shows that coordination without violence is possible.\ This is R&D of a new kind: based not on destruction, but digital creation.
Statement: Bitcoin isn’t “Gold 1.0,” but an improved version: divisible, verifiable, unseizable.
Criticism: Bitcoin has no physical value; "unseizability" is a theory;\ Gold is material and autonomous.
5. “Bitcoin Has No Physical Value”
And gold does? Just because it shines?
Physical form is no guarantee of value.\ Real value lies in: scarcity, reliable transfer, verifiability, and non-confiscatability.
Gold is:\ – Hard to divide\ – Hard to verify\ – Expensive to store\ – Easy to seize
💡 Bitcoin is the first store of value in history that is fully free from physical limitations, and yet:\ – Absolutely scarce (21M, forever)\ – Instantly transferable over the Internet\ – Cryptographically verifiable\ – Controlled by no government
🔑 Bitcoin’s value lies in its liberation from the physical.\ It doesn’t need to be “backed” by gold or oil. It’s backed by energy, mathematics, and ongoing verification.
“Price is what you pay, value is what you get.” — Warren Buffett
When you buy bitcoin, you’re not paying for a “token” — you’re gaining access to a network of distributed financial energy.
⚡️ What are you really getting when you own bitcoin?\ – A key to a digital asset that can’t be faked\ – The ability to send “crystallized energy” anywhere on Earth (it takes 10 minutes on the base L1 layer, or instantly via the Lightning Network)\ – A role in a new accounting system that runs 24/7/365\ – Freedom: from banks, borders, inflation, and force
📉 Bitcoin doesn’t require physical value — because it creates value:\ Through trust, scarcity, and energy invested in mining.\ And unlike gold, it was never associated with slavery.
Statement: There’s no “income without risk” in Bitcoin: just hold — you preserve; want more — invest, risk, build.
Criticism: contradicts HODL logic; speculation remains dominant behavior.
6. “Speculation Dominates”
For now — yes. That’s normal for the early phase of a new technology. Awareness doesn’t come instantly.
What matters is not the motive of today’s buyer — but what they’re buying.
📉 A speculator may come and go — but the asset remains.\ And this asset is the only one in history that will never exist again. 21 million. Forever.
📌 Look deeper. Bitcoin has:\ – No CEO\ – No central issuer\ – No inflation\ – No “off switch”\ 💡 It was fairly distributed — through mining, long before ASICs existed. In the early years, bitcoin was spent and exchanged — not hoarded. Only those who truly believed in it are still holding it today.
💡 It’s not a stock. Not a startup. Not someone’s project.\ It’s a new foundation for trust.\ It’s opting out of a system where freedom is a privilege you’re granted under conditions.
🧠 People say: “Bitcoin can be copied.”\ Theoretically — yes.\ Practically — never.
Here’s what you’d need to recreate Bitcoin:\ – No pre-mine\ – A founder who disappears and never sells\ – No foundation or corporation\ – Tens of thousands of nodes worldwide\ – 701 million terahashes of hash power\ – Thousands of devs writing open protocols\ – Hundreds of global conferences\ – Millions of people defending digital sovereignty\ – All that without a single marketing budget
That’s all.
🔁 Everything else is an imitation, not a creation.\ Just like you can’t “reinvent fire” — Bitcoin can only exist once.
Statements:\ **The Russia's '90s weren’t a free market — just anarchic chaos without rights protection.\ **Unlike fiat or even dollars, Bitcoin is the first asset with real defense — from governments, inflation, even thugs.\ *And yes, even if your barber asks about Bitcoin — maybe it's not a bubble, but a sign that inflation has already hit everyone.
Criticism: Bitcoin’s protection isn’t universal — it works only with proper handling and isn’t available to all.\ Some just want to “get rich.”\ None of this matters because:
-
Bitcoin’s volatility (-30% in a week, +50% in a month) makes it unusable for price planning or contracts.
-
It can’t handle mass-scale usage.
-
To become currency, geopolitical will is needed — and without the first two, don’t even talk about the third.\ Also: “Bitcoin is too complicated for the average person.”
7. “It’s Too Complex for the Masses”
It’s complex — if you’re using L1 (Layer 1). But even grandmas use Telegram. In El Salvador, schoolkids buy lunch with Lightning. My barber installed Wallet of Satoshi in minutes right in front of me — and I now pay for my haircut via Lightning.
UX is just a matter of time. And it’s improving. Emerging tools:\ Cashu, Fedimint, Fedi, Wallet of Satoshi, Phoenix, Proton Wallet, Swiss Bitcoin Pay, Bolt Card / CoinCorner (NFC cards for Lightning payments).
This is like the internet in 1995:\ It started with modems — now it’s 4K streaming.
💸 Now try sending a regular bank transfer abroad:\ – you need to type a long IBAN\ – add SWIFT/BIC codes\ – include the recipient’s full physical address (!), compromising their privacy\ – sometimes add extra codes or “purpose of payment”\ – you might get a call from your bank “just to confirm”\ – no way to check the status — the money floats somewhere between correspondent/intermediary banks\ – weekends or holidays? Banks are closed\ – and don’t forget the limits, restrictions, and potential freezes
📌 With Bitcoin, you just scan a QR code and send.\ 10 minutes on-chain = final settlement.\ Via Lightning = instant and nearly free.\ No bureaucracy. No permission. No borders.
8. “Can’t Handle the Load”
A common myth.\ Yes, Bitcoin L1 processes about 7 transactions per second — intentionally. It’s not built to be Visa. It’s a financial protocol, just like TCP/IP is a network protocol. TCP/IP isn’t “fast” or “slow” — the experience depends on the infrastructure built on top: servers, routers, hardware. In the ’90s, it delivered text. Today, it streams Netflix. The protocol didn’t change — the stack did.
Same with Bitcoin: L1 defines rules, security, finality.\ Scaling and speed? That’s the second layer’s job.
To understand scale:
| Network | TPS (Transactions/sec) | | --- | --- | | Visa | up to 24,000 | | Mastercard | \~5,000 | | PayPal | \~193 | | Litecoin | \~56 | | Ethereum | \~20 | | Bitcoin | \~7 |
\ ⚡️ Enter Lightning Network — Bitcoin’s “fast lane.”\ It allows millions of transactions per second, instantly and nearly free.
And it’s not a sidechain.
❗️ Lightning is not a separate network.\ It uses real Bitcoin transactions (2-of-2 multisig). You can close the channel to L1 at any time. It’s not an alternative — it’s a native extension built into Bitcoin.\ Also evolving: Ark, Fedimint, eCash — new ways to scale and add privacy.
📉 So criticizing Bitcoin for “slowness” is like blaming TCP/IP because your old modem won’t stream YouTube.\ The protocol isn’t the problem — it’s the infrastructure.
🛡️ And by the way: Visa crashes more often than Bitcoin.
9. “We Need Geopolitical Will”
Not necessarily. All it takes is the will of the people — and leaders willing to act. El Salvador didn’t wait for G20 approval or IMF blessings. Since 2001, the country had used the US dollar as its official currency, abandoning its own colón. But that didn’t save it from inflation or dependency on foreign monetary policy. In 2021, El Salvador became the first country to recognize Bitcoin as legal tender. Since March 13, 2024, they’ve been purchasing 1 BTC daily, tracked through their public address:
🔗 Address\ 📅 First transaction
This policy became the foundation of their Strategic Bitcoin Reserve (SBR) — a state-led effort to accumulate Bitcoin as a national reserve asset for long-term stability and sovereignty.
Their example inspired others.
In March 2025, U.S. President Donald Trump signed an executive order creating the Strategic Bitcoin Reserve of the USA, to be funded through confiscated Bitcoin and digital assets.\ The idea: accumulate, don’t sell, and strategically expand the reserve — without extra burden on taxpayers.
Additionally, Senator Cynthia Lummis (Wyoming) proposed the BITCOIN Act, targeting the purchase of 1 million BTC over five years (\~5% of the total supply).\ The plan: fund it via revaluation of gold certificates and other budget-neutral strategies.
📚 More: Strategic Bitcoin Reserve — Wikipedia
👉 So no global consensus is required. No IMF greenlight.\ All it takes is conviction — and an understanding that the future of finance lies in decentralized, scarce assets like Bitcoin.
10. “-30% in a week, +50% in a month = not money”
True — Bitcoin is volatile. But that’s normal for new technologies and emerging money. It’s not a bug — it’s a price discovery phase. The world is still learning what this asset is.
📉 Volatility is the price of entry.\ 📈 But the reward is buying the future at a discount.
As Michael Saylor put it:
“A tourist sees Niagara Falls as chaos — roaring, foaming, spraying water.\ An engineer sees immense energy.\ It all depends on your mental model.”
Same with Bitcoin. Speculators see chaos. Investors see structural scarcity. Builders see a new financial foundation.
💡 Now consider gold:
👉 After the gold standard was abandoned in 1971, the price of gold skyrocketed from around \~$300 to over $2,700 (adjusted to 2023 dollars) by 1980. Along the way, it experienced extreme volatility — with crashes of 40–60% even amid the broader uptrend.\ 💡 (\~$300 is the inflation-adjusted equivalent of about $38 in 1971 dollars)\ 📈 Source: Gold Price Chart — Macrotrends\ \ Nobody said, “This can’t be money.” \ Because money is defined not by volatility, but by scarcity, adoption, and trust — which build over time.
📊 The more people save in Bitcoin, the more its volatility fades.
This is a journey — not a fixed state.
We don’t judge the internet by how it worked in 1994.\ So why expect Bitcoin to be the “perfect currency” in 2025?
It grows bottom-up — without regulators’ permission.\ And the longer it survives, the stronger it becomes.
Remember how many times it’s been declared dead.\ And how many times it came back — stronger.
📊 Gold vs. Bitcoin: Supply Comparison
This chart shows the key difference between the two hard assets:
🔹 Gold — supply keeps growing.\ Mining may be limited, but it’s still inflationary.\ Each year, there’s more — with no known cap: new mines, asteroid mining, recycling.
🔸 Bitcoin — capped at 21 million.\ The emission schedule is public, mathematically predictable, and ends completely around 2140.
🧠 Bottom line:\ Gold is good.\ Bitcoin is better — for predictability and scarcity.
💡 As Saifedean Ammous said:
“Gold was the best monetary good… until Bitcoin.”
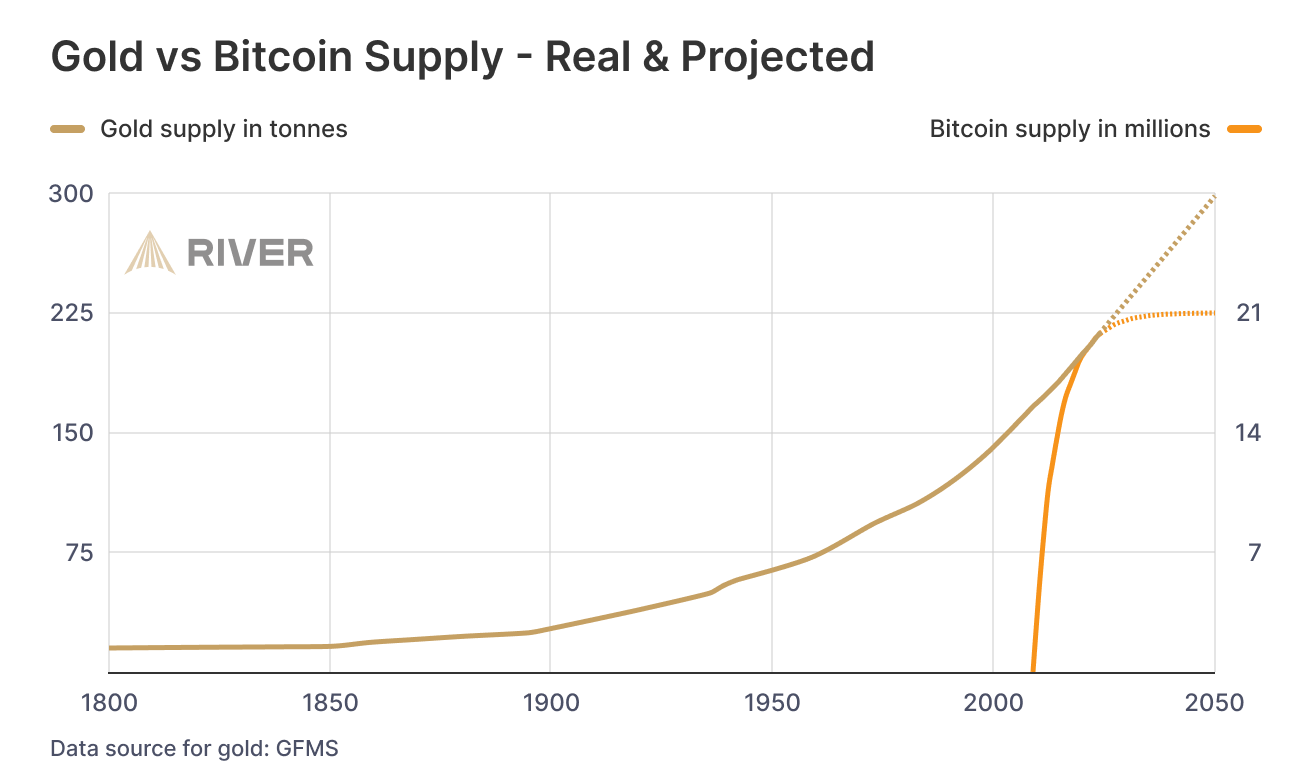 ### While we argue — fiat erodes every day.
### While we argue — fiat erodes every day.No matter your view on Bitcoin, just show me one other asset that is simultaneously:
– immune to devaluation by decree\ – impossible to print more of\ – impossible to confiscate by a centralized order\ – impossible to counterfeit\ – and, most importantly — transferable across borders without asking permission from a bank, a state, or a passport
💸 Try sending $10,000 through PayPal from Iran to Paraguay, or Bangladesh to Saint Lucia.\ Good luck. PayPal doesn't even work there.
Now open a laptop, type 12 words — and you have access to your savings anywhere on Earth.
🌍 Bitcoin doesn't ask for permission.\ It works for everyone, everywhere, all the time.
📌 There has never been anything like this before.
Bitcoin is the first asset in history that combines:
– digital nature\ – predictable scarcity\ – absolute portability\ – and immunity from tyranny
💡 As Michael Saylor said:
“Bitcoin is the first money in human history not created by bankers or politicians — but by engineers.”
You can own it with no bank.\ No intermediary.\ No passport.\ No approval.
That’s why Bitcoin isn’t just “internet money” or “crypto” or “digital gold.”\ It may not be perfect — but it’s incorruptible.\ And it’s not going away.\ It’s already here.\ It is the foundation of a new financial reality.
🔒 This is not speculation. This is a peaceful financial revolution.\ 🪙 This is not a stock. It’s money — like the world has never seen.\ ⛓️ This is not a fad. It’s a freedom protocol.
And when even the barber starts asking about Bitcoin — it’s not a bubble.\ It’s a sign that the system is breaking.\ And people are looking for an exit.
For the first time — they have one.
💼 This is not about investing. It’s about the dignity of work.
Imagine a man who cleans toilets at an airport every day.
Not a “prestigious” job.\ But a crucial one.\ Without him — filth, bacteria, disease.
He shows up on time. He works with his hands.
And his money? It devalues. Every day.
He doesn’t work less — often he works more than those in suits.\ But he can afford less and less — because in this system, honest labor loses value each year.
Now imagine he’s paid in Bitcoin.
Not in some “volatile coin,” but in hard money — with a limited supply.\ Money that can’t be printed, reversed, or devalued by central banks.
💡 Then he could:
– Stop rushing to spend, knowing his labor won’t be worth less tomorrow\ – Save for a dream — without fear of inflation eating it away\ – Feel that his time and effort are respected — because they retain value
Bitcoin gives anyone — engineer or janitor — a way out of the game rigged against them.\ A chance to finally build a future where savings are real.
This is economic justice.\ This is digital dignity.
📉 In fiat, you have to spend — or your money melts.\ 📈 In Bitcoin, you choose when to spend — because it’s up to you.
🧠 In a deflationary economy, both saving and spending are healthy:
You don’t scramble to survive — you choose to create.
🎯 That’s true freedom.
When even someone cleaning floors can live without fear —\ and know that their time doesn’t vanish... it turns into value.
🧱 The Bigger Picture
Bitcoin is not just a technology — it’s rooted in economic philosophy.\ The Austrian School of Economics has long argued that sound money, voluntary exchange, and decentralized decision-making are prerequisites for real prosperity.\ Bitcoin doesn’t reinvent these ideas — it makes them executable.
📉 Inflation doesn’t just erode savings.\ It quietly destroys quality of life.\ You work more — and everything becomes worse:\ – food is cheaper but less nutritious\ – homes are newer but uglier and less durable\ – clothes cost more but fall apart in months\ – streaming is faster, but your attention span collapses\ This isn’t just consumerism — it’s the economics of planned obsolescence.
🧨 Meanwhile, the U.S. debt has exceeded 3x its GDP.\ And nobody wants to buy U.S. bonds anymore — so the U.S. has to buy its own debt.\ Yes: printing money to buy the IOUs you just printed.\ This is the endgame of fiat.
🎭 Bonds are often sold as “safe.”\ But in practice, they are a weapon — especially abroad.\ The U.S. and IMF give loans to developing countries.\ But when those countries can’t repay (due to rigged terms or global economic headwinds), they’re forced to sell land, resources, or strategic assets.\ Both sides lose: the debtor collapses under the weight of debt, while the creditor earns resentment and instability.\ This isn’t cooperation — it’s soft colonialism enabled by inflation.
📌 Bitcoin offers a peaceful exit.\ A financial system where money can’t be created out of thin air.\ Where savings work.\ Where dignity is restored — even for those who clean toilets.
-
-
 @ 04c915da:3dfbecc9
2025-05-15 15:31:45
@ 04c915da:3dfbecc9
2025-05-15 15:31:45Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 58537364:705b4b85
2025-05-24 20:48:43
@ 58537364:705b4b85
2025-05-24 20:48:43“Any society that sets intellectual development as its goal will continually progress, without end—until life is liberated from problems and suffering. All problems can ultimately be solved through wisdom itself.
The signpost pointing toward ‘wisdom’ is the ability to think—or what is called in Dhamma terms, ‘yoniso-manasikāra,’ meaning wise or analytical reflection. Thinking is the bridge that connects information and knowledge with insight and understanding. Refined or skillful thinking enables one to seek knowledge and apply it effectively.
The key types of thinking are:
- Thinking to acquire knowledge
- Thinking to apply knowledge effectively In other words, thinking to gain knowledge and thinking to use that knowledge. A person with knowledge who doesn’t know how to think cannot make that knowledge useful. On the other hand, a person who thinks without having or seeking knowledge will end up with nothing but dreamy, deluded ideas. When such dreamy ideas are expressed as opinions, they become nonsensical and meaningless—mere expressions of personal likes or dislikes.
In this light, the ‘process of developing wisdom’ begins with the desire to seek knowledge, followed by the training of thinking skills, and concludes with the ability to express well-founded opinions. (In many important cases, practice, testing, or experimentation is needed to confirm understanding.)
Thus, the thirst for knowledge and the ability to seek knowledge are the forerunners of intellectual development. In any society where people lack a love for knowledge and are not inclined to search for it, true intellectual growth will be difficult. That society will be filled with fanciful, delusional thinking and opinions based merely on personal likes and dislikes. For the development of wisdom, there must be the guiding principle that: ‘Giving opinions must go hand-in-hand with seeking knowledge. And once knowledge is gained, thinking must be refined and skillful.’”
— Somdet Phra Buddhaghosacariya (P.A. Payutto) Source: Dhamma treatise “Organizing Society According to the Ideals of the Sangha”
Note: “Pariyosāna” means the complete conclusion or the final, all-encompassing end.
“We must emphasize the pursuit of knowledge more than merely giving opinions. Opinions must be based on the most solid foundation of knowledge.
Nowadays, we face so many problems because people love to express opinions without ever seeking knowledge.”
— Somdet Phra Buddhaghosacariya (P.A. Payutto)
-
 @ 3f770d65:7a745b24
2025-01-12 21:03:36
@ 3f770d65:7a745b24
2025-01-12 21:03:36I’ve been using Notedeck for several months, starting with its extremely early and experimental alpha versions, all the way to its current, more stable alpha releases. The journey has been fascinating, as I’ve had the privilege of watching it evolve from a concept into a functional and promising tool.
In its earliest stages, Notedeck was raw—offering glimpses of its potential but still far from practical for daily use. Even then, the vision behind it was clear: a platform designed to redefine how we interact with Nostr by offering flexibility and power for all users.
I'm very bullish on Notedeck. Why? Because Will Casarin is making it! Duh! 😂
Seriously though, if we’re reimagining the web and rebuilding portions of the Internet, it’s important to recognize the potential of Notedeck. If Nostr is reimagining the web, then Notedeck is reimagining the Nostr client.
Notedeck isn’t just another Nostr app—it’s more a Nostr browser that functions more like an operating system with micro-apps. How cool is that?
Much like how Google's Chrome evolved from being a web browser with a task manager into ChromeOS, a full blown operating system, Notedeck aims to transform how we interact with the Nostr. It goes beyond individual apps, offering a foundation for a fully integrated ecosystem built around Nostr.
As a Nostr evangelist, I love to scream INTEROPERABILITY and tout every application's integrations. Well, Notedeck has the potential to be one of the best platforms to showcase these integrations in entirely new and exciting ways.
Do you want an Olas feed of images? Add the media column.
Do you want a feed of live video events? Add the zap.stream column.
Do you want Nostr Nests or audio chats? Add that column to your Notedeck.
Git? Email? Books? Chat and DMs? It's all possible.
Not everyone wants a super app though, and that’s okay. As with most things in the Nostr ecosystem, flexibility is key. Notedeck gives users the freedom to choose how they engage with it—whether it’s simply following hashtags or managing straightforward feeds. You'll be able to tailor Notedeck to fit your needs, using it as extensively or minimally as you prefer.
Notedeck is designed with a local-first approach, utilizing Nostr content stored directly on your device via the local nostrdb. This will enable a plethora of advanced tools such as search and filtering, the creation of custom feeds, and the ability to develop personalized algorithms across multiple Notedeck micro-applications—all with unparalleled flexibility.
Notedeck also supports multicast. Let's geek out for a second. Multicast is a method of communication where data is sent from one source to multiple destinations simultaneously, but only to devices that wish to receive the data. Unlike broadcast, which sends data to all devices on a network, multicast targets specific receivers, reducing network traffic. This is commonly used for efficient data distribution in scenarios like streaming, conferencing, or large-scale data synchronization between devices.
In a local first world where each device holds local copies of your nostr nodes, and each device transparently syncs with each other on the local network, each node becomes a backup. Your data becomes antifragile automatically. When a node goes down it can resync and recover from other nodes. Even if not all nodes have a complete collection, negentropy can pull down only what is needed from each device. All this can be done without internet.
-Will Casarin
In the context of Notedeck, multicast would allow multiple devices to sync their Nostr nodes with each other over a local network without needing an internet connection. Wild.
Notedeck aims to offer full customization too, including the ability to design and share custom skins, much like Winamp. Users will also be able to create personalized columns and, in the future, share their setups with others. This opens the door for power users to craft tailored Nostr experiences, leveraging their expertise in the protocol and applications. By sharing these configurations as "Starter Decks," they can simplify onboarding and showcase the best of Nostr’s ecosystem.
Nostr’s “Other Stuff” can often be difficult to discover, use, or understand. Many users doesn't understand or know how to use web browser extensions to login to applications. Let's not even get started with nsecbunkers. Notedeck will address this challenge by providing a native experience that brings these lesser-known applications, tools, and content into a user-friendly and accessible interface, making exploration seamless. However, that doesn't mean Notedeck should disregard power users that want to use nsecbunkers though - hint hint.
For anyone interested in watching Nostr be developed live, right before your very eyes, Notedeck’s progress serves as a reminder of what’s possible when innovation meets dedication. The current alpha is already demonstrating its ability to handle complex use cases, and I’m excited to see how it continues to grow as it moves toward a full release later this year.
-
 @ 21810ca8:f2e8341e
2025-05-25 05:02:33
@ 21810ca8:f2e8341e
2025-05-25 05:02:33If so, please comment. So I can see if Nostr works for me.
-
 @ eb0157af:77ab6c55
2025-05-25 04:48:11
@ eb0157af:77ab6c55
2025-05-25 04:48:11Michigan lawmakers are unveiling a comprehensive strategy to regulate Bitcoin and cryptocurrencies.
On May 21, Republican Representative Bill Schuette introduced House Bill 4510, a proposal to amend the Michigan Public Employee Retirement System Investment Act. The legislation would allow the state treasurer, currently Rachael Eubanks, to diversify the state’s investments by including cryptocurrencies with an average market capitalization of over $250 million in the past calendar year.
Under current criteria, Bitcoin (BTC) and Ether (ETH) are the only cryptocurrencies that meet these selection standards. The proposal specifies that any investment in digital assets must be made through exchange-traded products (spot ETFs) issued by registered investment companies.
Anti-CBDC legislation
Republican Representative Bryan Posthumus is leading the bipartisan initiative behind the second bill, HB 4511, which establishes protections for cryptocurrency holders. The proposal prohibits Michigan from implementing crypto bans or imposing licensing requirements on digital asset holders.
Another key aspect of the legislation is a ban on state officials from supporting or promoting a potential federal central bank digital currency (CBDC). The definition includes the issuance of memorandums or official statements endorsing CBDC proposals related to testing, adoption, or implementation.
Mining and redevelopment of abandoned sites
The third bill, HB 4512, is a proposal led by Democratic Representative Mike McFall for a bipartisan group. This initiative would establish a Bitcoin mining program allowing operators to use abandoned oil and natural gas sites.
The program calls for the appointment of a supervisor tasked with assessing the site’s remaining productive potential, identifying the last operator, and determining the length of abandonment. Prospective participants would need to submit detailed legal documentation of their organizational structure, demonstrate operational expertise in mining, and provide profitability breakeven estimates for their ventures.
The fourth and final bill, HB 4513, also introduced by the bipartisan group led by McFall, focuses on the fiscal aspect of the HB 4512 initiative. The proposal would amend Michigan’s income tax laws to include proceeds generated from the proposed Bitcoin mining program.
The post Michigan: four bills on pension funds, CBDCs, and mining appeared first on Atlas21.
-
 @ cefb08d1:f419beff
2025-05-21 10:15:18
@ cefb08d1:f419beff
2025-05-21 10:15:18Cat angels are the reason there are no mice angels.
Mel Brooks
https://stacker.news/items/985375
-
 @ eb0157af:77ab6c55
2025-05-25 04:48:10
@ eb0157af:77ab6c55
2025-05-25 04:48:10A fake Uber driver steals $73,000 in XRP and $50,000 in Bitcoin after drugging an American tourist.
A U.S. citizen vacationing in the United Kingdom fell victim to a scam that cost him $123,000 in cryptocurrencies stored on his smartphone. The man was drugged by an individual posing as an Uber driver.
According to My London, Jacob Irwin-Cline had spent the evening at a London nightclub, consuming several alcoholic drinks before requesting an Uber ride home. The victim admitted he hadn’t carefully verified the booking details on his device, mistakenly getting into a private taxi driven by someone who, at first glance, resembled the expected Uber driver but was using a completely different vehicle.
Once inside the car, the American tourist reported that the driver offered him a cigarette, allegedly laced with scopolamine — a rare and powerful sedative. Irwin-Cline described how the smoke made him extremely docile and fatigued, causing him to lose consciousness for around half an hour.
Upon waking, the driver ordered the victim to get out of the vehicle. As Irwin-Cline stepped out, the man suddenly accelerated, running him over and fleeing with his mobile phone, which contained the private keys and access to his cryptocurrencies. Screenshots provided to MyLondon show that $73,000 worth of XRP and $50,000 in bitcoin had been transferred to various wallets.
This incident adds to a growing trend of kidnappings, extortions, armed robberies, and ransom attempts targeting crypto executives, investors, and their families.
Just a few weeks ago, the daughter and grandson of Pierre Noizat, CEO of crypto exchange Paymium, were targeted in a kidnapping attempt in Paris. The incident took place in broad daylight when attackers tried to force the family into a parked vehicle. However, Noizat’s daughter managed to fight off the assailants.
The post American tourist drugged and robbed: $123,000 in crypto stolen in London appeared first on Atlas21.
-
 @ 95543309:196c540e
2025-05-11 12:42:09
@ 95543309:196c540e
2025-05-11 12:42:09Lets see if this works with the blossom upload and without markdown hassle.
:cat:

https://blossom.primal.net/73a099f931366732c18dd60da82db6ef65bb368eb96756f07d9fa7a8a3644009.mp4
-
 @ 95cbd62b:a5270126
2025-05-24 14:06:33
@ 95cbd62b:a5270126
2025-05-24 14:06:33Trong thời đại công nghệ số phát triển mạnh mẽ, nhu cầu tìm kiếm một nền tảng tích hợp đầy đủ tiện ích, an toàn và thân thiện với người dùng ngày càng tăng cao. OK22 đã chứng minh vị thế của mình không chỉ là một nền tảng giải trí trực tuyến, mà còn là một công cụ công nghệ thông minh phục vụ mọi nhu cầu trong đời sống số. Với thiết kế giao diện 100% tiếng Việt và khả năng tương thích trên mọi thiết bị từ máy tính đến điện thoại, OK22 mang đến cho người dùng trải nghiệm mượt mà, dễ sử dụng và hoàn toàn bảo mật. Được phát triển trên nền tảng công nghệ hiện đại, OK22 hỗ trợ người dùng quản lý thông tin cá nhân, thực hiện giao dịch nhanh chóng, lưu trữ dữ liệu an toàn và tiếp cận các tiện ích công nghệ tiên tiến một cách dễ dàng, kể cả với người mới sử dụng.
Một trong những điểm mạnh nổi bật của OK22 chính là khả năng tự động hóa trong xử lý tác vụ, giúp tiết kiệm thời gian và tối ưu hóa hiệu suất làm việc. Nền tảng được trang bị hệ thống bảo mật cao cấp, bảo vệ tối đa quyền riêng tư và tài sản số của người dùng. OK22 còn cung cấp hệ thống hỗ trợ trực tuyến 24/7, giúp người dùng giải quyết mọi vấn đề nhanh chóng mà không bị gián đoạn. Dù là một cá nhân đang tìm kiếm công cụ quản lý tài chính cá nhân, một doanh nghiệp nhỏ cần nền tảng để xử lý đơn hàng và thanh toán, hay một nhóm cộng đồng cần không gian kết nối số – OK22 đều có thể đáp ứng linh hoạt và hiệu quả. Không những vậy, nhờ tích hợp nhiều tính năng như thông báo tự động, đồng bộ dữ liệu đám mây, và tích hợp API mở, OK22 còn dễ dàng kết nối với các nền tảng khác trong hệ sinh thái số, giúp người dùng tạo nên một môi trường làm việc và sinh hoạt thông minh.
Không dừng lại ở đó, OK22 đang ngày càng mở rộng hợp tác với các đối tác lớn trong nhiều lĩnh vực như giáo dục trực tuyến, thương mại điện tử, chăm sóc sức khỏe và tài chính cá nhân. Nền tảng không ngừng cập nhật những công nghệ tiên tiến như AI, blockchain và dữ liệu lớn (Big Data) nhằm mang lại trải nghiệm người dùng tối ưu và đáp ứng nhu cầu ngày càng đa dạng của cộng đồng Việt. Với tốc độ xử lý nhanh, giao diện trực quan và độ tin cậy cao, OK22 không chỉ đơn thuần là một ứng dụng công nghệ – mà còn là người bạn đồng hành tin cậy trong hành trình số hóa của người Việt. Trong tương lai gần, OK22 hứa hẹn sẽ trở thành nền tảng công nghệ không thể thiếu trong mỗi gia đình, tổ chức và doanh nghiệp, đóng vai trò then chốt trong việc thúc đẩy chuyển đổi số toàn diện và phát triển bền vững.
-
 @ cefb08d1:f419beff
2025-05-21 09:02:28
@ cefb08d1:f419beff
2025-05-21 09:02:28https://www.youtube.com/watch?v=OOmr2s-JPXo
The GWM Catch Up Day 3: Men's Quarterfinalists Locked, The Box delivers for pro surfing’s faithful:
https://www.youtube.com/watch?v=Owe-rjECP3M
The Box dishes West Oz power, Main Break decides last Quarters draws I Stone & Wood Post Show Day 3:
https://www.youtube.com/watch?v=qN3oi4kOGAA
Men 16 Round Results:
Source: https://www.worldsurfleague.com/events/2025/ct/326/western-australia-margaret-river-pro/results?roundId=24776
https://stacker.news/items/985339
-
 @ f6488c62:c929299d
2025-05-24 05:10:20
@ f6488c62:c929299d
2025-05-24 05:10:20คุณเคยจินตนาการถึงอนาคตที่ AI มีความฉลาดเทียบเท่ามนุษย์หรือไม่? นี่คือสิ่งที่ Sam Altman ซีอีโอของ OpenAI และทีมพันธมิตรอย่าง SoftBank, Oracle และ MGX กำลังผลักดันผ่าน โครงการ Stargate! โครงการนี้ไม่ใช่แค่เรื่องเทคโนโลยี แต่เป็นก้าวกระโดดครั้งใหญ่ของมนุษยชาติ! Stargate คืออะไร? Stargate เป็นโปรเจกต์สร้าง ศูนย์ข้อมูล AI ขนาดยักษ์ที่ใหญ่ที่สุดในประวัติศาสตร์ ด้วยเงินลงทุนเริ่มต้น 100,000 ล้านดอลลาร์ และอาจสูงถึง 500,000 ล้านดอลลาร์ ภายในปี 2029! เป้าหมายคือการพัฒนา Artificial General Intelligence (AGI) หรือ AI ที่ฉลาดเทียบเท่ามนุษย์ เพื่อให้สหรัฐฯ ครองความเป็นผู้นำด้าน AI และแข่งขันกับคู่แข่งอย่างจีน โครงการนี้เริ่มต้นที่เมือง Abilene รัฐเท็กซัส โดยจะสร้างศูนย์ข้อมูล 10 แห่ง และขยายไปยังญี่ปุ่น สหราชอาณาจักร และสหรัฐอาหรับเอมิเรตส์ ทำไม Stargate ถึงสำคัญ?
นวัตกรรมเปลี่ยนโลก: AI จาก Stargate จะช่วยพัฒนาวัคซีน mRNA รักษามะเร็งได้ใน 48 ชั่วโมง และยกระดับอุตสาหกรรมต่าง ๆ เช่น การแพทย์และความมั่นคงแห่งชาติสร้างงาน: คาดว่าจะสร้างงานกว่า 100,000 ตำแหน่ง ในสหรัฐฯ
พลังงานมหาศาล: ศูนย์ข้อมูลอาจใช้พลังงานถึง 1.2 กิกะวัตต์ เทียบเท่ากับเมืองขนาดใหญ่!
ใครอยู่เบื้องหลัง? Sam Altman ร่วมมือกับ Masayoshi Son จาก SoftBank และได้รับการสนับสนุนจาก Donald Trump ซึ่งผลักดันนโยบายให้ Stargate เป็นจริง การก่อสร้างดำเนินการโดย Oracle และพันธมิตรด้านพลังงานอย่าง Crusoe Energy Systems ความท้าทาย? ถึงจะยิ่งใหญ่ แต่ Stargate ก็เจออุปสรรค ทั้งปัญหาการระดมทุน ความกังวลเรื่องภาษีนำเข้าชิป และการแข่งขันจากคู่แข่งอย่าง DeepSeek ที่ใช้โครงสร้างพื้นฐานน้อยกว่า แถม Elon Musk ยังออกมาวิจารณ์ว่าโครงการนี้อาจ “ไม่สมจริง” แต่ Altman มั่นใจและเชิญ Musk ไปดูไซต์งานที่เท็กซัสเลยทีเดียว! อนาคตของ Stargate ศูนย์ข้อมูลแห่งแรกจะเริ่มใช้งานในปี 2026 และอาจเปลี่ยนโฉมวงการ AI ไปตลอดกาล นี่คือก้าวสำคัญสู่ยุคใหม่ของเทคโนโลยีที่อาจเปลี่ยนวิถีชีวิตของเรา! และไม่ใช่ประตูดวงดาวแบบในหนังนะ! ถึงชื่อ Stargate จะได้แรงบันดาลใจจากภาพยนตร์ sci-fi อันโด่งดัง แต่โครงการนี้ไม่ได้พาเราไปยังดวงดาวอื่น มันคือการเปิดประตูสู่โลกแห่ง AI ที่ทรงพลัง และอาจเปลี่ยนอนาคตของมนุษยชาติไปเลย! และไม่เหมือน universechain ของ star ของผมนะครับ
Stargate #AI #SamAltman #OpenAI #อนาคตของเทคโนโลยี
-
 @ cefb08d1:f419beff
2025-05-21 06:34:00
@ cefb08d1:f419beff
2025-05-21 06:34:00https://stacker.news/items/985298
-
 @ 7460b7fd:4fc4e74b
2025-05-21 02:35:36
@ 7460b7fd:4fc4e74b
2025-05-21 02:35:36如果比特币发明了真正的钱,那么 Crypto 是什么?
引言
比特币诞生之初就以“数字黄金”姿态示人,被支持者誉为人类历史上第一次发明了真正意义上的钱——一种不依赖国家信用、总量恒定且不可篡改的硬通货。然而十多年过去,比特币之后蓬勃而起的加密世界(Crypto)已经远超“货币”范畴:从智能合约平台到去中心组织,从去央行的稳定币到戏谑荒诞的迷因币,Crypto 演化出一个丰富而混沌的新生态。这不禁引发一个根本性的追问:如果说比特币解决了“真金白银”的问题,那么 Crypto 又完成了什么发明?
 Crypto 与政治的碰撞:随着Crypto版图扩张,全球政治势力也被裹挟进这场金融变革洪流(示意图)。比特币的出现重塑了货币信用,但Crypto所引发的却是一场更深刻的政治与治理结构实验。从华尔街到华盛顿,从散户论坛到主权国家,越来越多人意识到:Crypto不只是技术或金融现象,而是一种全新的政治表达结构正在萌芽。正如有激进论者所断言的:“比特币发明了真正的钱,而Crypto则在发明新的政治。”价格K线与流动性曲线,或许正成为这个时代社群意志和社会价值观的新型投射。
Crypto 与政治的碰撞:随着Crypto版图扩张,全球政治势力也被裹挟进这场金融变革洪流(示意图)。比特币的出现重塑了货币信用,但Crypto所引发的却是一场更深刻的政治与治理结构实验。从华尔街到华盛顿,从散户论坛到主权国家,越来越多人意识到:Crypto不只是技术或金融现象,而是一种全新的政治表达结构正在萌芽。正如有激进论者所断言的:“比特币发明了真正的钱,而Crypto则在发明新的政治。”价格K线与流动性曲线,或许正成为这个时代社群意志和社会价值观的新型投射。冲突结构:当价格挑战选票
传统政治中,选票是人民意志的载体,一人一票勾勒出民主治理的正统路径。而在链上的加密世界里,骤升骤降的价格曲线和真金白银的买卖行为却扮演起了选票的角色:资金流向成了民意走向,市场多空成为立场表决。价格行为取代选票,这听来匪夷所思,却已在Crypto社群中成为日常现实。每一次代币的抛售与追高,都是社区对项目决策的即时“投票”;每一根K线的涨跌,都折射出社区意志的赞同或抗议。市场行为本身承担了决策权与象征权——价格即政治,正在链上蔓延。
这一新生政治形式与旧世界的民主机制形成了鲜明冲突。bitcoin.org中本聪在比特币白皮书中提出“一CPU一票”的工作量证明共识,用算力投票取代了人为决策bitcoin.org。而今,Crypto更进一步,用资本市场的涨跌来取代传统政治的选举。支持某项目?直接购入其代币推高市值;反对某提案?用脚投票抛售资产。相比漫长的选举周期和层层代议制,链上市场提供了近乎实时的“公投”机制。但这种机制也引发巨大争议:资本的投票天然偏向持币多者(富者)的意志,是否意味着加密政治更为金权而非民权?持币多寡成为影响力大小,仿佛选举演变成了“一币一票”,巨鲸富豪俨然掌握更多话语权。这种与民主平等原则的冲突,成为Crypto政治形式饱受质疑的核心张力之一。
尽管如此,我们已经目睹市场投票在Crypto世界塑造秩序的威力:2016年以太坊因DAO事件分叉时,社区以真金白银“投票”决定了哪条链获得未来。arkhamintelligence.com结果是新链以太坊(ETH)成为主流,其市值一度超过2,800亿美元,而坚持原则的以太经典(ETC)市值不足35亿美元,不及前者的八十分之一arkhamintelligence.com。市场选择清楚地昭示了社区的政治意志。同样地,在比特币扩容之争、各类硬分叉博弈中,无不是由投资者和矿工用资金与算力投票,胜者存续败者黯然。价格成为裁决纷争的最终选票,冲击着传统“选票决胜”的政治理念。Crypto的价格民主,与现代代议民主正面相撞,激起当代政治哲思中前所未有的冲突火花。
治理与分配
XRP对决SEC成为了加密世界“治理与分配”冲突的经典战例。2020年底,美国证券交易委员会(SEC)突然起诉Ripple公司,指控其发行的XRP代币属于未注册证券,消息一出直接引爆市场恐慌。XRP价格应声暴跌,一度跌去超过60%,最低触及0.21美元coindesk.com。曾经位居市值前三的XRP险些被打入谷底,监管的强硬姿态似乎要将这个项目彻底扼杀。
然而XRP社区没有选择沉默。 大批长期持有者组成了自称“XRP军团”(XRP Army)的草根力量,在社交媒体上高调声援Ripple,对抗监管威胁。面对SEC的指控,他们集体发声,质疑政府选择性执法,声称以太坊当年发行却“逍遥法外”,只有Ripple遭到不公对待coindesk.com。正如《福布斯》的评论所言:没人预料到愤怒的加密散户投资者会掀起法律、政治和社交媒体领域的‘海啸式’反击,痛斥监管机构背弃了保护投资者的承诺crypto-law.us。这种草根抵抗监管的话语体系迅速形成:XRP持有者不但在网上掀起舆论风暴,还采取实际行动向SEC施压。他们发起了请愿,抨击SEC背离保护投资者初衷、诉讼给个人投资者带来巨大伤害,号召停止对Ripple的上诉纠缠——号称这是在捍卫全球加密用户的共同利益bitget.com。一场由民间主导的反监管运动就此拉开帷幕。
Ripple公司则选择背水一战,拒绝和解,在法庭上与SEC针锋相对地鏖战了近三年之久。Ripple坚称XRP并非证券,不应受到SEC管辖,即使面临沉重法律费用和业务压力也不妥协。2023年,这场持久战迎来了标志性转折:美国法庭作出初步裁决,认定XRP在二级市场的流通不构成证券coindesk.com。这一胜利犹如给沉寂已久的XRP注入强心针——消息公布当天XRP价格飙涨近一倍,盘中一度逼近1美元大关coindesk.com。沉重监管阴影下苟延残喘的项目,凭借司法层面的突破瞬间重获生机。这不仅是Ripple的胜利,更被支持者视为整个加密行业对SEC强权的一次胜仗。
XRP的对抗路线与某些“主动合规”的项目形成了鲜明对比。 稳定币USDC的发行方Circle、美国最大合规交易所Coinbase等选择了一条迎合监管的道路:它们高调拥抱现行法规,希望以合作换取生存空间。然而现实却给了它们沉重一击。USDC稳定币在监管风波中一度失去美元锚定,哪怕Circle及时披露储备状况也无法阻止恐慌蔓延,大批用户迅速失去信心,短时间内出现数十亿美元的赎回潮blockworks.co。Coinbase则更为直接:即便它早已注册上市、反复向监管示好,2023年仍被SEC指控为未注册证券交易所reuters.com,卷入漫长诉讼漩涡。可见,在迎合监管的策略下,这些机构非但未能换来监管青睐,反而因官司缠身或用户流失而丧失市场信任。 相比之下,XRP以对抗求生存的路线反而赢得了投资者的眼光:价格的涨跌成为社区投票的方式,抗争的勇气反过来强化了市场对它的信心。
同样引人深思的是另一种迥异的治理路径:技术至上的链上治理。 以MakerDAO为代表的去中心化治理模式曾被寄予厚望——MKR持币者投票决策、算法维持稳定币Dai的价值,被视为“代码即法律”的典范。然而,这套纯技术治理在市场层面却未能形成广泛认同,亦无法激发群体性的情绪动员。复杂晦涩的机制使得普通投资者难以参与其中,MakerDAO的治理讨论更多停留在极客圈子内部,在社会大众的政治对话中几乎听不见它的声音。相比XRP对抗监管所激发的铺天盖地关注,MakerDAO的治理实验显得默默无闻、难以“出圈”。这也说明,如果一种治理实践无法连接更广泛的利益诉求和情感共鸣,它在社会政治层面就难以形成影响力。
XRP之争的政治象征意义由此凸显: 它展示了一条“以市场对抗国家”的斗争路线,即通过代币价格的集体行动来回应监管权力的施压。在这场轰动业界的对决中,价格即是抗议的旗帜,涨跌映射着政治立场。XRP对SEC的胜利被视作加密世界向旧有权力宣告的一次胜利:资本市场的投票器可以撼动监管者的强权。这种“价格即政治”的张力,正是Crypto世界前所未有的社会实验:去中心化社区以市场行为直接对抗国家权力,在无形的价格曲线中凝聚起政治抗争的力量,向世人昭示加密货币不仅有技术和资本属性,更蕴含着不可小觑的社会能量和政治意涵。
不可归零的政治资本
Meme 币的本质并非廉价或易造,而在于其构建了一种“无法归零”的社群生存结构。 对于传统观点而言,多数 meme 币只是短命的投机游戏:价格暴涨暴跌后一地鸡毛,创始人套现跑路,投资者血本无归,然后“大家转去炒下一个”theguardian.com。然而,meme 币社群的独特之处在于——失败并不意味着终结,而更像是运动的逗号而非句号。一次币值崩盘后,持币的草根们往往并未散去;相反,他们汲取教训,准备东山再起。这种近乎“不死鸟”的循环,使得 meme 币运动呈现出一种数字政治循环的特质:价格可以归零,但社群的政治热情和组织势能不归零。正如研究者所指出的,加密领域中的骗局、崩盘等冲击并不会摧毁生态,反而成为让系统更加强韧的“健康应激”,令整个行业在动荡中变得更加反脆弱cointelegraph.com。对应到 meme 币,每一次暴跌和重挫,都是社群自我进化、卷土重来的契机。这个去中心化群体打造出一种自组织的安全垫,失败者得以在瓦砾上重建家园。对于草根社群、少数派乃至体制的“失败者”而言,meme 币提供了一个永不落幕的抗争舞台,一种真正反脆弱的政治性。正因如此,我们看到诸多曾被嘲笑的迷因项目屡败屡战:例如 Dogecoin 自2013年问世后历经八年沉浮,早已超越玩笑属性,成为互联网史上最具韧性的迷因之一frontiersin.org;支撑 Dogecoin 的正是背后强大的迷因文化和社区意志,它如同美国霸权支撑美元一样,为狗狗币提供了“永不中断”的生命力frontiersin.org。
“复活权”的数字政治意涵
这种“失败-重生”的循环结构蕴含着深刻的政治意涵:在传统政治和商业领域,一个政党选举失利或一家公司破产往往意味着清零出局,资源散尽、组织瓦解。然而在 meme 币的世界,社群拥有了一种前所未有的“复活权”。当项目崩盘,社区并不必然随之消亡,而是可以凭借剩余的人心和热情卷土重来——哪怕换一个 token 名称,哪怕重启一条链,运动依然延续。正如 Cheems 项目的核心开发者所言,在几乎无人问津、技术受阻的困境下,大多数人可能早已卷款走人,但 “CHEEMS 社区没有放弃,背景、技术、风投都不重要,重要的是永不言弃的精神”cointelegraph.com。这种精神使得Cheems项目起死回生,社区成员齐声宣告“我们都是 CHEEMS”,共同书写历史cointelegraph.com。与传统依赖风投和公司输血的项目不同,Cheems 完全依靠社区的信念与韧性存续发展,体现了去中心化运动的真谛cointelegraph.com。这意味着政治参与的门槛被大大降低:哪怕没有金主和官方背书,草根也能凭借群体意志赋予某个代币新的生命。对于身处社会边缘的群体来说,meme 币俨然成为自组织的安全垫和重新集结的工具。难怪有学者指出,近期涌入meme币浪潮的主力,正是那些对现实失望但渴望改变命运的年轻人theguardian.com——“迷茫的年轻人,想要一夜暴富”theguardian.com。meme币的炒作表面上看是投机赌博,但背后蕴含的是草根对既有金融秩序的不满与反抗:没有监管和护栏又如何?一次失败算不得什么,社区自有后路和新方案。这种由底层群众不断试错、纠错并重启的过程,本身就是一种数字时代的新型反抗运动和群众动员机制。
举例而言,Terra Luna 的沉浮充分展现了这种“复活机制”的政治力量。作为一度由风投资本热捧的项目,Luna 币在2022年的崩溃本可被视作“归零”的失败典范——稳定币UST瞬间失锚,Luna币价归零,数十亿美元灰飞烟灭。然而“崩盘”并没有画下休止符。Luna的残余社区拒绝承认失败命运,通过链上治理投票毅然启动新链,“复活”了 Luna 代币,再次回到市场交易reuters.com。正如 Terra 官方在崩盘后发布的推文所宣称:“我们力量永在社区,今日的决定正彰显了我们的韧性”reuters.com。事实上,原链更名为 Luna Classic 后,大批所谓“LUNC 军团”的散户依然死守阵地,誓言不离不弃;他们自发烧毁巨量代币以缩减供应、推动技术升级,试图让这个一度归零的项目重新燃起生命之火binance.com。失败者并未散场,而是化作一股草根洪流,奋力托举起项目的残迹。经过迷因化的叙事重塑,这场从废墟中重建价值的壮举,成为加密世界中草根政治的经典一幕。类似的案例不胜枚举:曾经被视为笑话的 DOGE(狗狗币)正因多年社群的凝聚而跻身主流币种,总市值一度高达数百亿美元,充分证明了“民有民享”的迷因货币同样可以笑傲市场frontiersin.org。再看最新的美国政治舞台,连总统特朗普也推出了自己的 meme 币 $TRUMP,号召粉丝拿真金白银来表达支持。该币首日即从7美元暴涨至75美元,两天后虽回落到40美元左右,但几乎同时,第一夫人 Melania 又发布了自己的 $Melania 币,甚至连就职典礼的牧师都跟风发行了纪念币theguardian.com!显然,对于狂热的群众来说,一个币的沉浮并非终点,而更像是运动的换挡——资本市场成为政治参与的新前线,你方唱罢我登场,meme 币的群众动员热度丝毫不减。值得注意的是,2024年出现的 Pump.fun 等平台更是进一步降低了这一循环的技术门槛,任何人都可以一键生成自己的 meme 币theguardian.com。这意味着哪怕某个项目归零,剩余的社区完全可以借助此类工具迅速复制一个新币接力,延续集体行动的火种。可以说,在 meme 币的世界里,草根社群获得了前所未有的再生能力和主动权,这正是一种数字时代的群众政治奇观:失败可以被当作梗来玩,破产能够变成重生的序章。
价格即政治:群众投机的新抗争
meme 币现象的兴盛表明:在加密时代,价格本身已成为一种政治表达。这些看似荒诞的迷因代币,将金融市场变成了群众宣泄情绪和诉求的另一个舞台。有学者将此概括为“将公民参与直接转化为了投机资产”cdn-brighterworld.humanities.mcmaster.ca——也就是说,社会运动的热情被注入币价涨跌,政治支持被铸造成可以交易的代币。meme 币融合了金融、技术与政治,通过病毒般的迷因文化激发公众参与,形成对现实政治的某种映射cdn-brighterworld.humanities.mcmaster.caosl.com。当一群草根投入全部热忱去炒作一枚毫无基本面支撑的币时,这本身就是一种大众政治动员的体现:币价暴涨,意味着一群人以戏谑的方式在向既有权威叫板;币价崩盘,也并不意味着信念的消亡,反而可能孕育下一次更汹涌的造势。正如有分析指出,政治类 meme 币的出现前所未有地将群众文化与政治情绪融入市场行情,价格曲线俨然成为民意和趋势的风向标cdn-brighterworld.humanities.mcmaster.ca。在这种局面下,投机不再仅仅是逐利,还是一种宣示立场、凝聚共识的过程——一次次看似荒唐的炒作背后,是草根对传统体制的不服与嘲讽,是失败者拒绝认输的呐喊。归根结底,meme 币所累积的,正是一种不可被归零的政治资本。价格涨落之间,群众的愤怒、幽默与希望尽显其中;这股力量不因一次挫败而消散,反而在市场的循环中愈发壮大。也正因如此,我们才说“价格即政治”——在迷因币的世界里,价格不只是数字,更是人民政治能量的晴雨表,哪怕归零也终将卷土重来。cdn-brighterworld.humanities.mcmaster.caosl.com
全球新兴现象:伊斯兰金融的入场
当Crypto在西方世界掀起市场治政的狂潮时,另一股独特力量也悄然融入这一场域:伊斯兰金融携其独特的道德秩序,开始在链上寻找存在感。长期以来,伊斯兰金融遵循着一套区别于世俗资本主义的原则:禁止利息(Riba)、反对过度投机(Gharar/Maysir)、强调实际资产支撑和道德投资。当这些原则遇上去中心化的加密技术,会碰撞出怎样的火花?出人意料的是,这两者竟在“以市场行为表达价值”这个层面产生了惊人的共鸣。伊斯兰金融并不拒绝市场机制本身,只是为其附加了道德准则;Crypto则将市场机制推向了政治高位,用价格来表达社群意志。二者看似理念迥异,实则都承认市场行为可以也应当承载社会价值观。这使得越来越多金融与政治分析人士开始关注:当虔诚的宗教伦理遇上狂野的加密市场,会塑造出何种新范式?
事实上,穆斯林世界已经在探索“清真加密”的道路。一些区块链项目致力于确保协议符合伊斯兰教法(Sharia)的要求。例如Haqq区块链发行的伊斯兰币(ISLM),从规则层面内置了宗教慈善义务——每发行新币即自动将10%拨入慈善DAO,用于公益捐赠,以符合天课(Zakat)的教义nasdaq.comnasdaq.com。同时,该链拒绝利息和赌博类应用,2022年还获得了宗教权威的教令(Fatwa)认可其合规性nasdaq.com。再看理念层面,伊斯兰经济学强调货币必须有内在价值、收益应来自真实劳动而非纯利息剥削。这一点与比特币的“工作量证明”精神不谋而合——有人甚至断言法定货币无锚印钞并不清真,而比特币这类需耗费能源生产的资产反而更符合教法初衷cointelegraph.com。由此,越来越多穆斯林投资者开始以道德投资的名义进入Crypto领域,将资金投向符合清真原则的代币和协议。
这种现象带来了微妙的双重合法性:一方面,Crypto世界原本奉行“价格即真理”的世俗逻辑,而伊斯兰金融为其注入了一股道德合法性,使部分加密资产同时获得了宗教与市场的双重背书;另一方面,即便在遵循宗教伦理的项目中,最终决定成败的依然是市场对其价值的认可。道德共识与市场共识在链上交汇,共同塑造出一种混合的新秩序。这一全球新兴现象引发广泛议论:有人将其视为金融民主化的极致表现——不同文化价值都能在市场平台上表达并竞争;也有人警惕这可能掩盖新的风险,因为把宗教情感融入高风险资产,既可能凝聚强大的忠诚度,也可能在泡沫破裂时引发信仰与财富的双重危机。但无论如何,伊斯兰金融的入场使Crypto的政治版图更加丰盈多元。从华尔街交易员到中东教士,不同背景的人们正通过Crypto这个奇特的舞台,对人类价值的表达方式进行前所未有的实验。
升华结语:价格即政治的新直觉
回顾比特币问世以来的这段历程,我们可以清晰地看到一条演进的主线:先有货币革命,后有政治发明。比特币赋予了人类一种真正自主的数字货币,而Crypto在此基础上完成的,则是一项前所未有的政治革新——它让市场价格行为承担起了类似政治选票的功能,开创了一种“价格即政治”的新直觉。在这个直觉下,市场不再只是冷冰冰的交易场所;每一次资本流动、每一轮行情涨落,都被赋予了社会意义和政治涵义。买入即表态,卖出即抗议,流动性的涌入或枯竭胜过千言万语的陈情。Crypto世界中,K线图俨然成为民意曲线,行情图就是政治晴雨表。决策不再由少数权力精英关起门来制定,而是在全球无眠的交易中由无数普通人共同谱写。这样的政治形式也许狂野,也许充满泡沫和噪音,但它不可否认地调动起了广泛的社会参与,让原本疏离政治进程的个体通过持币、交易重新找回了影响力的幻觉或实感。
“价格即政治”并非一句简单的口号,而是Crypto给予世界的全新想象力。它质疑了传统政治的正统性:如果一串代码和一群匿名投资者就能高效决策资源分配,我们为何还需要繁冗的官僚体系?它也拷问着自身的内在隐忧:当财富与权力深度绑定,Crypto政治如何避免堕入金钱统治的老路?或许,正是在这样的矛盾和张力中,人类政治的未来才会不断演化。Crypto所开启的,不仅是技术乌托邦或金融狂欢,更可能是一次对民主形式的深刻拓展和挑战。这里有最狂热的逐利者,也有最理想主义的社群塑梦者;有一夜暴富的神话,也有瞬间破灭的惨痛。而这一切汇聚成的洪流,正冲撞着工业时代以来既定的权力谱系。
当我们再次追问:Crypto究竟是什么? 或许可以这样回答——Crypto是比特币之后,人类完成的一次政治范式的试验性跃迁。在这里,价格行为化身为选票,资本市场演化为广场,代码与共识共同撰写“社会契约”。这是一场仍在进行的文明实验:它可能无声地融入既有秩序,也可能剧烈地重塑未来规则。但无论结局如何,如今我们已经见证:在比特币发明真正的货币之后,Crypto正在发明真正属于21世纪的政治。它以数字时代的语言宣告:在链上,价格即政治,市场即民意,代码即法律。这,或许就是Crypto带给我们的最直观而震撼的本质启示。
参考资料:
-
中本聪. 比特币白皮书: 一种点对点的电子现金系统. (2008)bitcoin.org
-
Arkham Intelligence. Ethereum vs Ethereum Classic: Understanding the Differences. (2023)arkhamintelligence.com
-
Binance Square (@渔神的加密日记). 狗狗币价格为何上涨?背后的原因你知道吗?binance.com
-
Cointelegraph中文. 特朗普的迷因币晚宴预期内容揭秘. (2025)cn.cointelegraph.com
-
慢雾科技 Web3Caff (@Lisa). 风险提醒:从 LIBRA 看“政治化”的加密货币骗局. (2025)web3caff.com
-
Nasdaq (@Anthony Clarke). How Cryptocurrency Aligns with the Principles of Islamic Finance. (2023)nasdaq.comnasdaq.com
-
Cointelegraph Magazine (@Andrew Fenton). DeFi can be halal but not DOGE? Decentralizing Islamic finance. (2023)cointelegraph.com
-
-
 @ eb0157af:77ab6c55
2025-05-25 04:48:09
@ eb0157af:77ab6c55
2025-05-25 04:48:09Banking giants JPMorgan, Bank of America, Citigroup, and Wells Fargo are in talks to develop a unified stablecoin solution.
According to the Wall Street Journal on May 22, some of the largest financial institutions in the United States are exploring the possibility of joining forces to launch a stablecoin.
Subsidiaries of JPMorgan, Bank of America, Citigroup, and Wells Fargo have initiated preliminary discussions for a joint stablecoin issuance, according to sources close to the matter cited by the WSJ. Also at the negotiating table are Early Warning Services, the parent company of the digital payments network Zelle, and the payment network Clearing House.
The talks are reportedly still in the early stages, and any final decision could change depending on regulatory developments and market demand for stablecoins.
Stablecoin regulation
On May 20, the US Senate voted 66 to 32 to advance discussion of the Guiding and Establishing National Innovation for US Stablecoins Act (GENIUS Act), a specific law to regulate stablecoins. The bill outlines a regulatory framework for stablecoin collateralization and mandates compliance with anti-money laundering rules.
David Sacks, White House crypto advisor, expressed optimism about the bill’s bipartisan approval. However, senior Democratic Party officials intend to amend the bill to include a clause preventing former President Donald Trump and other US officials from profiting from stablecoins.
Demand for stablecoins has increased, with total market capitalization rising to $245 billion from $205 billion at the beginning of the year, a 20% increase.
The post Major US banks consider launching a joint stablecoin appeared first on Atlas21.
-
 @ 211c0393:e9262c4d
2025-05-25 04:00:34
@ 211c0393:e9262c4d
2025-05-25 04:00:34Original: https://www.yakihonne.com/article/naddr1qvzqqqr4gupzqgguqwf52cyve89xnxc4eh95jklelgw646kkkcdhxm4fp05jvtzdqq2hj6fhtpqkuutdv4xxxazjv9t92atedev45mcwusz
Nihon no kakuseizai Nihon no kakusei-zai bijinesu no yami: Keisatsu, bōryokudan, soshite
chinmoku no kyōhan kankei' no shinsō** 1. Bōryokudan no shihai kōzō (kōteki dēta ni motodzuku) yunyū izon no riyū: Kokunai seizō wa kon'nan (Heisei 6-nenkakusei-zai genryō kisei-hō' de kisei kyōka)→ myanmā Chūgoku kara no mitsuyu ga shuryū (Kokuren yakubutsu hanzai jimushoWorld Drug Report 2023'). Bōryokudan no rieki-ritsu: 1 Kg-atari shiire kakaku 30 man-en → kouri kakaku 500 man ~ 1000 man-en (Keisatsuchōyakubutsu jōsei hōkoku-sho' 2022-nen). 2. Keisatsu to bōryokudan nokyōsei kankei' taiho tōkei no fushizen-sa: Zen yakubutsu taiho-sha no 70-pāsento ga tanjun shoji (kōsei Rōdōshōyakubutsu ran'yō jōkyō' 2023-nen). Mitsuyu soshiki no tekihatsu wa zentai no 5-pāsento-miman (tōkyōchikentokusōbu dēta). Media no kenshō: NHK supesharukakusei-zai sensō'(2021-nen) de shiteki sa retamattan yūzā yūsen sōsa' no jittai. 3. Mujun suru genjitsu juyō no fukashi-sei: G 7 de saikō no kakusei-zai kakaku (1 g-atari 3 ~ 7 man-en, Ō kome no 3-bai)→ bōryokudan no bōri (Zaimushōsoshiki hanzai shikin ryūdō chōsa'). Shiyōsha-ritsu wa hikui (jinkō no 0. 2%, Kokuren chōsa) ga, taiho-sha no kahansū o shimeru mujun. 4.Mitsuyu soshiki taisaku' no genkai kokusai-tekina shippai rei: Mekishiko (karuteru tekihatsu-go mo ichiba kakudai), Ōshū (gōsei yakubutsu no man'en)→ daitai soshiki ga sokuza ni taitō (Eiekonomisuto' 2023-nen 6 tsuki-gō). Nippon'nochiri-teki hande: Kaijō mitsuyu no tekihatsu-ritsu wa 10-pāsento-miman (Kaijōhoanchō hōkoku). 5. Kaiketsusaku no saikō (jijitsu ni motodzuku teian) ADHD chiryō-yaku no gōhō-ka: Amerika seishin'igakukaiADHD kanja no 60-pāsento ga jiko chiryō de ihō yakubutsu shiyō'(2019-nen kenkyū). Nihonde wa ritarin aderōru kinshi → bōryokudan no ichiba dokusen. Rōdō kankyō kaikaku: Karō-shi rain koe no rōdō-sha 20-pāsento (Kōrōshōrōdō jikan chōsa' 2023-nen)→ kakusei-zai juyō no ichiin. 6. Kokuhatsu no risuku to jōhō-gen tokumei-sei no jūyō-sei: Kako no bōryokudan hōfuku jirei (2018-nen, kokuhatsu kisha e no kyōhaku jiken Mainichishinbun hōdō). Kōteki dēta nomi in'yō: Rei:Keisatsuchō tōkei'Kokuren hōkoku-sho' nado daisansha kenshō kanōna jōhō. Ketsuron: Henkaku no tame ni wajijitsu' no kajika ga hitsuyō `yakubutsu = kojin no dōtokuteki mondai' to iu gensō ga, bōryokudan to fuhai kanryō o ri shite iru. Kokusai dēta to kokunai tōkei no mujun o tsuku koto de, shisutemu no giman o abakeru. Anzen'na kyōyū no tame ni: Kojin tokutei o sake, tokumei purattofōmu (tōa-jō fōramu-tō) de giron. Kōteki kikan no dēta o chokusetsu rinku (rei: Keisatsuchō PDF repōto). Kono bunsho wa, kōhyō sa reta tōkei media hōdō nomi o konkyo to shi, kojin no suisoku o haijo shite imasu. Kyōi o yokeru tame, gutaitekina kojin soshiki no hinan wa itotekini sakete imasu. Show more 1,321 / 5,000 Stimulants in Japan The dark side of the Japanese stimulant drug business:The truth about the police, the yakuza, and their "silent complicity"**
- The control structure of the yakuza (based on public data)
Reasons for dependence on imports: Domestic production is difficult (tightened regulations under the Stimulant Drug Raw Materials Control Act of 1994) → Smuggling from Myanmar and China is the norm (UNODC World Drug Report 2023).
Profit margins for yakuza: Purchase price of 300,000 yen per kg → Retail price of 5 to 10 million yen (National Police Agency Drug Situation Report 2022).
- The "symbiotic relationship" between the police and the yakuza
The unnaturalness of arrest statistics: 70% of all drug arrests are for simple possession (Ministry of Health, Labor and Welfare Drug Abuse Situation 2023). Smuggling organizations account for less than 5% of all arrests (Tokyo District Public Prosecutors Office Special Investigation Unit data). Media verification: The reality of "end-user priority investigation" pointed out in the NHK special "Stimulant War" (2021).
- Contradictory reality
Invisibility of demand: The highest stimulant drug price in the G7 (30,000 to 70,000 yen per gram, three times that of Europe and the United States) → Excessive profits by organized crime (Ministry of Finance "Survey on Organized Crime Fund Flows"). The contradiction that the user rate is low (0.2% of the population, UN survey), but accounts for the majority of arrests.
- The limits of "countermeasures against smuggling organizations"
International examples of failure: Mexico (market expands even after cartel crackdown), Europe (proliferation of synthetic drugs) → Alternative organizations immediately emerge (UK "The Economist" June 2023 issue). Japan's geographical handicap: The crackdown rate for maritime smuggling is less than 10% (Japan Coast Guard report).
- Rethinking solutions (fact-based proposals)
Legalization of ADHD medications:
American Psychiatric Association: "60% of ADHD patients self-medicate with illegal drugs" (2019 study).
Banning Ritalin and Adderall in Japan → Yakuza monopoly on the market.
Work environment reform:
20% of workers exceed the line of death from overwork (Ministry of Health, Labor and Welfare "Working Hours Survey" 2023) → One cause of stimulant drug demand.
- Risks of accusation and sources of information
Importance of anonymity:
Past cases of Yakuza retaliation (2018, threat against accusing journalist, reported in the Mainichi Shimbun).
Citing only public data:
Examples: Information that can be verified by a third party, such as "National Police Agency statistics" and "UN reports".
Conclusion: Visualization of "facts" is necessary for change
The illusion that "drugs = individual moral problems" benefits Yakuza and corrupt bureaucrats.
Pointing out the contradictions between international data and domestic statistics can expose the deception of the system.
For safe sharing:
Avoid identifying individuals and discuss on anonymous platforms (such as forums on Tor).
Direct links to data from public organizations (e.g. National Police Agency PDF report).
This document is based solely on published statistics and media reports, and excludes personal speculation.
To avoid threats, we have intentionally avoided blaming specific individuals or organizations. Send feedback
-
 @ c1d77557:bf04ec8b
2025-05-24 05:02:26
@ c1d77557:bf04ec8b
2025-05-24 05:02:26O 567br é uma plataforma de entretenimento online que tem se destacado pela sua inovação, variedade de jogos e foco na experiência do jogador. Com uma interface amigável e recursos de alta qualidade, a plataforma oferece uma jornada divertida e segura para os seus usuários. Neste artigo, vamos explorar os principais aspectos do 567br, incluindo a introdução da plataforma, os jogos que ela oferece e como a experiência do jogador é aprimorada em cada detalhe.
O 567br foi desenvolvido com o objetivo de proporcionar aos jogadores uma experiência imersiva e prazerosa. Sua interface é simples, intuitiva e de fácil navegação, permitindo que os usuários encontrem rapidamente seus jogos favoritos. A plataforma também é otimizada para dispositivos móveis, o que significa que os jogadores podem acessar seus jogos em qualquer lugar e a qualquer momento, seja no computador ou no smartphone.
Além disso, o 567brse preocupa com a segurança de seus usuários, implementando tecnologias de criptografia de ponta para garantir que todos os dados pessoais e financeiros estejam protegidos. A plataforma também oferece suporte ao cliente de alta qualidade, disponível 24/7, para resolver quaisquer dúvidas ou problemas que possam surgir durante a experiência de jogo.
Jogos Empolgantes e Variedade para Todos os Gostos No 567br, a diversidade de jogos é um dos pontos fortes da plataforma. Desde jogos de mesa e cartas até opções de entretenimento mais dinâmicas e inovadoras, há algo para todos os gostos e preferências. Os jogos disponíveis são desenvolvidos por alguns dos melhores fornecedores de conteúdo da indústria, garantindo gráficos de alta qualidade, jogabilidade fluida e mecânicas envolventes.
Os jogadores podem escolher entre diferentes categorias, como:
Jogos de Mesa: Para quem gosta de uma experiência mais estratégica e de tomada de decisões, os jogos de mesa são uma excelente opção. São oferecidas diversas variantes de jogos populares, como pôquer, blackjack, roleta, entre outros.
Jogos de Ação e Aventura: Para os que buscam adrenalina e emoção, a plataforma oferece uma seleção de jogos de ação e aventura com temas envolventes e gráficos impressionantes. Esses jogos garantem uma experiência de jogo emocionante e desafiadora.
Jogos de Arcade: Se você está em busca de algo mais descontraído e divertido, os jogos de arcade são uma excelente escolha. Eles são rápidos, fáceis de entender e proporcionam diversão instantânea.
A plataforma está sempre atualizando seu portfólio de jogos para garantir que os jogadores tenham acesso às últimas novidades e inovações do mundo do entretenimento online.
A Experiência do Jogador: Personalização e Interatividade O 567br não se limita a oferecer apenas uma plataforma de jogos, mas também busca criar uma experiência personalizada e interativa para cada jogador. A plataforma possui funcionalidades que permitem que os usuários ajustem sua experiência de jogo de acordo com suas preferências individuais.
A personalização da interface é um exemplo claro disso. O jogador pode escolher o tema e a disposição dos elementos na tela, criando um ambiente que seja confortável e agradável de usar. Além disso, o 567br oferece recursos interativos, como chats ao vivo, onde os jogadores podem interagir com outros usuários e até mesmo com os dealers, proporcionando uma sensação de comunidade.
Outro aspecto importante é a possibilidade de acompanhar o desempenho e os resultados de jogo. A plataforma oferece relatórios detalhados, permitindo que os jogadores monitorem seu progresso, analisem suas vitórias e perdas, e façam ajustes em sua estratégia de jogo.
Promoções e Benefícios para os Jogadores O 567br também oferece uma série de promoções e benefícios que tornam a experiência de jogo ainda mais atrativa. Novos jogadores podem aproveitar bônus de boas-vindas e outras ofertas especiais, enquanto jogadores regulares podem se beneficiar de programas de fidelidade e promoções exclusivas.
Essas ofertas ajudam a aumentar a diversão e proporcionam mais oportunidades para que os jogadores explorem novos jogos e tenham uma experiência ainda mais rica. Além disso, o sistema de recompensas é transparente e justo, garantindo que todos os jogadores tenham as mesmas oportunidades de aproveitar os benefícios.
Conclusão: Uma Plataforma Completa para Todos os Gostos Com sua interface intuitiva, variedade de jogos e foco na experiência do jogador, o 567br se consolida como uma plataforma de entretenimento online de alta qualidade. Seja para quem busca jogos estratégicos, ação intensa ou diversão casual, o 567br tem algo para todos.
A segurança, o suporte ao cliente e a personalização da experiência de jogo tornam o 567br uma opção atraente para jogadores que buscam mais do que apenas uma plataforma de jogos – buscam uma jornada de entretenimento envolvente e segura. Se você está procurando por uma experiência completa e agradável, o 567br é, sem dúvida, uma excelente escolha.
-
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 2b998b04:86727e47
2025-05-25 03:28:59
@ 2b998b04:86727e47
2025-05-25 03:28:59Turning 60
Ten years ago, I turned 50 with a vague sense that something was off.
I was building things, but they didn’t feel grounded.\ I was "in tech," but tech felt like a treadmill—just faster, sleeker tools chasing the same hollow outcomes.\ I knew about Bitcoin, but I dismissed it. I thought it was just “tech for tech’s sake.”
Less than a year later, I fell down the rabbit hole.
It didn’t happen all at once. At first it was curiosity. Then dissonance. Then conviction.
Somewhere in that process, I realized Bitcoin wasn’t just financial—it was philosophical. It was moral. It was real. And it held up a mirror to a life I had built on momentum more than mission.
So I started pruning.
I left Web3.\ I pulled back from projects that ran on hype instead of honesty.\ I repented—for chasing relevance instead of righteousness.\ And I began stacking—not just sats, but new habits. New thinking. New rhythms of faith, work, and rest.
Now at 60, I’m not where I thought I’d be.
But I’m more myself than I’ve ever been.\ More convicted.\ More rooted.\ More ready.
Not to start over—but to build again, from the foundation up.
If you're in that middle place—between chapters, between convictions, between certainty and surrender—you're not alone.
🟠 I’m still here. Still building. Still listening.
Zap if this resonates, or send your story. I’d love to hear it.
[*Zap *](https://tinyurl.com/yuyu2b9t)
-
 @ 52b4a076:e7fad8bd
2025-05-03 21:54:45
@ 52b4a076:e7fad8bd
2025-05-03 21:54:45Introduction
Me and Fishcake have been working on infrastructure for Noswhere and Nostr.build. Part of this involves processing a large amount of Nostr events for features such as search, analytics, and feeds.
I have been recently developing
nosdexv3, a newer version of the Noswhere scraper that is designed for maximum performance and fault tolerance using FoundationDB (FDB).Fishcake has been working on a processing system for Nostr events to use with NB, based off of Cloudflare (CF) Pipelines, which is a relatively new beta product. This evening, we put it all to the test.
First preparations
We set up a new CF Pipelines endpoint, and I implemented a basic importer that took data from the
nosdexdatabase. This was quite slow, as it did HTTP requests synchronously, but worked as a good smoke test.Asynchronous indexing
I implemented a high-contention queue system designed for highly parallel indexing operations, built using FDB, that supports: - Fully customizable batch sizes - Per-index queues - Hundreds of parallel consumers - Automatic retry logic using lease expiration
When the scraper first gets an event, it will process it and eventually write it to the blob store and FDB. Each new event is appended to the event log.
On the indexing side, a
Queuerwill read the event log, and batch events (usually 2K-5K events) into one work job. This work job contains: - A range in the log to index - Which target this job is intended for - The size of the job and some other metadataEach job has an associated leasing state, which is used to handle retries and prioritization, and ensure no duplication of work.
Several
Workers monitor the index queue (up to 128) and wait for new jobs that are available to lease.Once a suitable job is found, the worker acquires a lease on the job and reads the relevant events from FDB and the blob store.
Depending on the indexing type, the job will be processed in one of a number of ways, and then marked as completed or returned for retries.
In this case, the event is also forwarded to CF Pipelines.
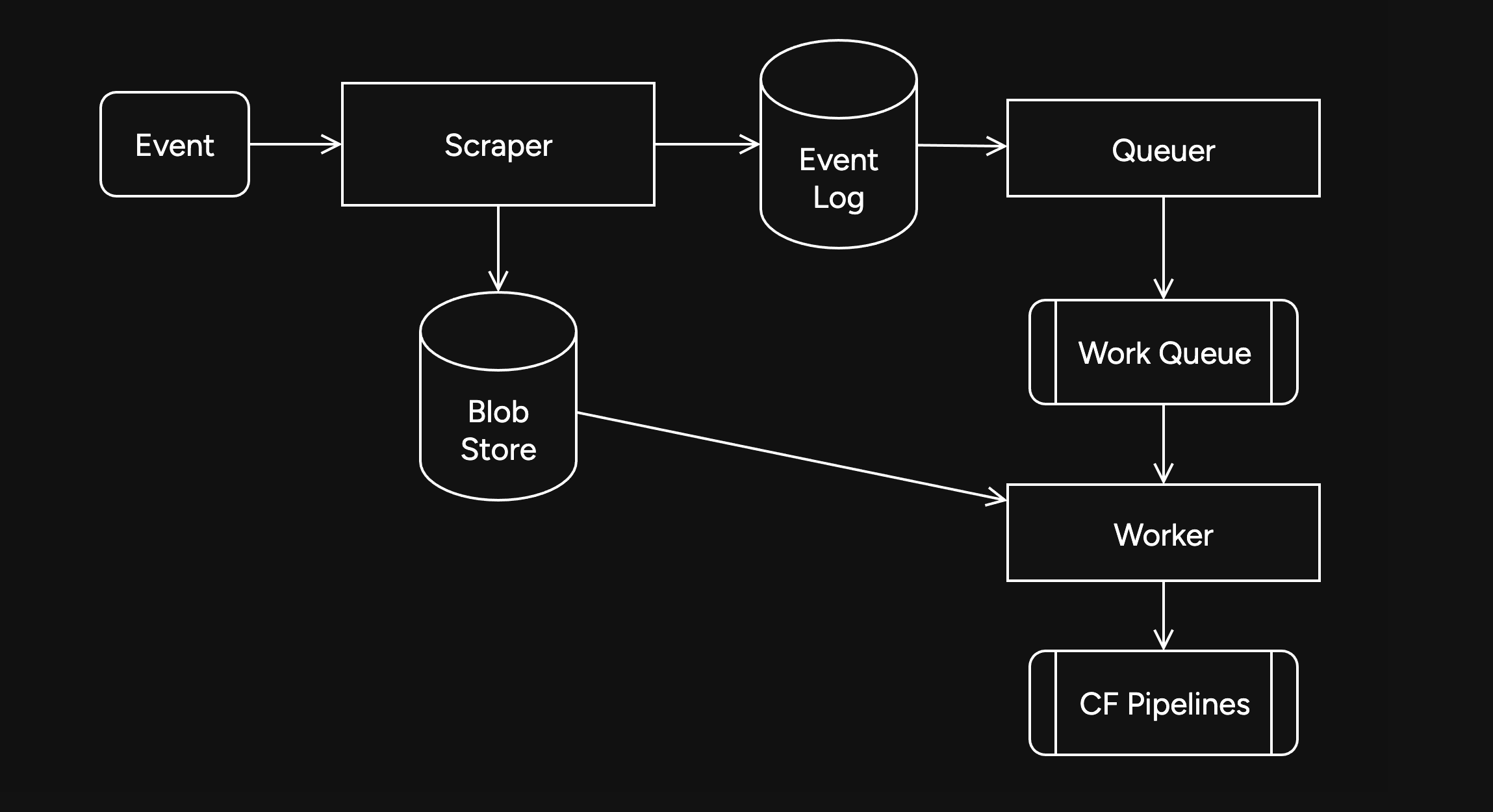
Trying it out
The first attempt did not go well. I found a bug in the high-contention indexer that led to frequent transaction conflicts. This was easily solved by correcting an incorrectly set parameter.
We also found there were other issues in the indexer, such as an insufficient amount of threads, and a suspicious decrease in the speed of the
Queuerduring processing of queued jobs.Along with fixing these issues, I also implemented other optimizations, such as deprioritizing
WorkerDB accesses, and increasing the batch size.To fix the degraded
Queuerperformance, I ran the backfill job by itself, and then started indexing after it had completed.Bottlenecks, bottlenecks everywhere

After implementing these fixes, there was an interesting problem: The DB couldn't go over 80K reads per second. I had encountered this limit during load testing for the scraper and other FDB benchmarks.
As I suspected, this was a client thread limitation, as one thread seemed to be using high amounts of CPU. To overcome this, I created a new client instance for each
Worker.After investigating, I discovered that the Go FoundationDB client cached the database connection. This meant all attempts to create separate DB connections ended up being useless.
Using
OpenWithConnectionStringpartially resolved this issue. (This also had benefits for service-discovery based connection configuration.)To be able to fully support multi-threading, I needed to enabled the FDB multi-client feature. Enabling it also allowed easier upgrades across DB versions, as FDB clients are incompatible across versions:
FDB_NETWORK_OPTION_EXTERNAL_CLIENT_LIBRARY="/lib/libfdb_c.so"FDB_NETWORK_OPTION_CLIENT_THREADS_PER_VERSION="16"Breaking the 100K/s reads barrier
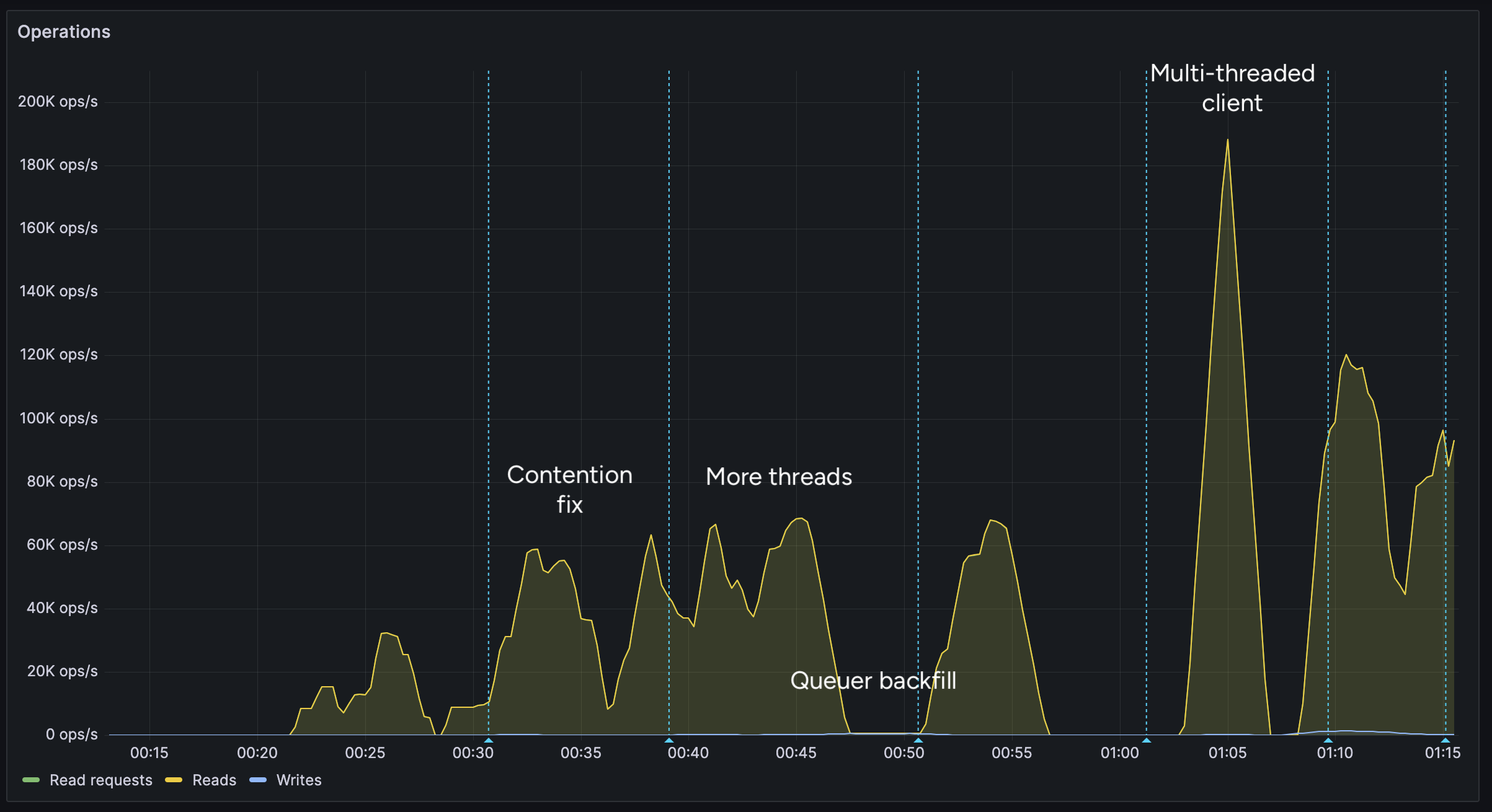
After implementing support for the multi-threaded client, we were able to get over 100K reads per second.
You may notice after the restart (gap) the performance dropped. This was caused by several bugs: 1. When creating the CF Pipelines endpoint, we did not specify a region. The automatically selected region was far away from the server. 2. The amount of shards were not sufficient, so we increased them. 3. The client overloaded a few HTTP/2 connections with too many requests.
I implemented a feature to assign each
Workerits own HTTP client, fixing the 3rd issue. We also moved the entire storage region to West Europe to be closer to the servers.After these changes, we were able to easily push over 200K reads/s, mostly limited by missing optimizations:
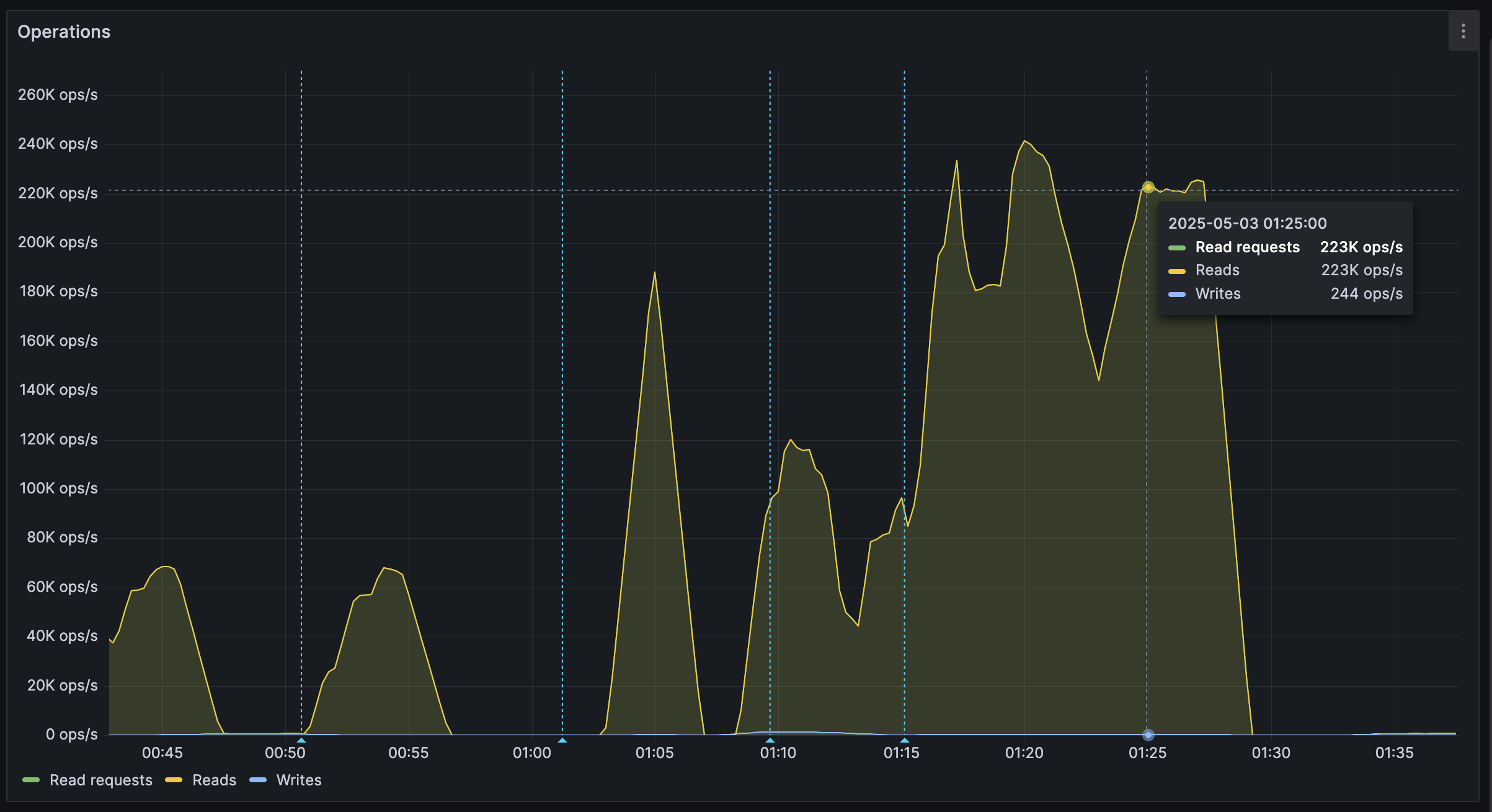
It's shards all the way down
While testing, we also noticed another issue: At certain times, a pipeline would get overloaded, stalling requests for seconds at a time. This prevented all forward progress on the
Workers.We solved this by having multiple pipelines: A primary pipeline meant to be for standard load, with moderate batching duration and less shards, and high-throughput pipelines with more shards.
Each
Workeris assigned a pipeline on startup, and if one pipeline stalls, other workers can continue making progress and saturate the DB.The stress test
After making sure everything was ready for the import, we cleared all data, and started the import.
The entire import lasted 20 minutes between 01:44 UTC and 02:04 UTC, reaching a peak of: - 0.25M requests per second - 0.6M keys read per second - 140MB/s reads from DB - 2Gbps of network throughput
FoundationDB ran smoothly during this test, with: - Read times under 2ms - Zero conflicting transactions - No overloaded servers
CF Pipelines held up well, delivering batches to R2 without any issues, while reaching its maximum possible throughput.

Finishing notes
Me and Fishcake have been building infrastructure around scaling Nostr, from media, to relays, to content indexing. We consistently work on improving scalability, resiliency and stability, even outside these posts.
Many things, including what you see here, are already a part of Nostr.build, Noswhere and NFDB, and many other changes are being implemented every day.
If you like what you are seeing, and want to integrate it, get in touch. :)
If you want to support our work, you can zap this post, or register for nostr.land and nostr.build today.
-
 @ 266815e0:6cd408a5
2025-05-02 22:24:59
@ 266815e0:6cd408a5
2025-05-02 22:24:59Its been six long months of refactoring code and building out to the applesauce packages but the app is stable enough for another release.
This update is pretty much a full rewrite of the non-visible parts of the app. all the background services were either moved out to the applesauce packages or rewritten, the result is that noStrudel is a little faster and much more consistent with connections and publishing.
New layout
The app has a new layout now, it takes advantage of the full desktop screen and looks a little better than it did before.
Removed NIP-72 communities
The NIP-72 communities are no longer part of the app, if you want to continue using them there are still a few apps that support them ( like satellite.earth ) but noStrudel won't support them going forward.
The communities where interesting but ultimately proved too have some fundamental flaws, most notably that all posts had to be approved by a moderator. There were some good ideas on how to improve it but they would have only been patches and wouldn't have fixed the underlying issues.
I wont promise to build it into noStrudel, but NIP-29 (relay based groups) look a lot more promising and already have better moderation abilities then NIP-72 communities could ever have.
Settings view
There is now a dedicated settings view, so no more hunting around for where the relays are set or trying to find how to add another account. its all in one place now
Cleaned up lists
The list views are a little cleaner now, and they have a simple edit modal
New emoji picker
Just another small improvement that makes the app feel more complete.
Experimental Wallet
There is a new "wallet" view in the app that lets you manage your NIP-60 cashu wallet. its very experimental and probably won't work for you, but its there and I hope to finish it up so the app can support NIP-61 nutzaps.
WARNING: Don't feed the wallet your hard earned sats, it will eat them!
Smaller improvements
- Added NSFW flag for replies
- Updated NIP-48 bunker login to work with new spec
- Linkfy BIPs
- Added 404 page
- Add NIP-22 comments under badges, files, and articles
- Add max height to timeline notes
- Fix articles view freezing on load
- Add option to mirror blobs when sharing notes
- Remove "open in drawer" for notes
-
 @ 3f770d65:7a745b24
2025-05-20 21:14:28
@ 3f770d65:7a745b24
2025-05-20 21:14:28I’m Derek Ross, and I’m all-in on Nostr.
I started the Grow Nostr Initiative to help more people discover what makes Nostr so powerful: ✅ You own your identity ✅ You choose your social graph and algorithms ✅ You aren't locked into any single app or platform ✅ You can post, stream, chat, and build, all without gatekeepers
What we’re doing with Grow Nostr Initiative: 🌱 Hosting local meetups and mini-conferences to onboard people face-to-face 📚 Creating educational materials and guides to demystify how Nostr works 🧩 Helping businesses and creators understand how they can plug into Nostr (running media servers, relays, and using key management tools)
I believe Nostr is the foundation of a more open internet. It’s still early, but we’re already seeing incredible apps for social, blogging, podcasting, livestreaming, and more. And the best part is that they're all interoperable, censorship-resistant, and built on open standards. Nostr is the world's largest bitcoin economy by transaction volume and I truly believe that the purple pill helps the orange pill go down. Meaning, growing Nostr will also grow Bitcoin adoption.
If you’ve been curious about Nostr or are building something on it, or let’s talk. Whether you're just getting started or you're already deep in the ecosystem, I'm here to answer questions, share what I’ve learned, and hear your ideas. Check out https://nostrapps.com to find your next social decentralized experience.
Ask Me Anything about GNI, Nostr, Bitcoin, the upcoming #NosVegas event at the Bitcoin Conference next week, etc.!
– Derek Ross 🌐 https://grownostr.org npub18ams6ewn5aj2n3wt2qawzglx9mr4nzksxhvrdc4gzrecw7n5tvjqctp424
https://stacker.news/items/984689
-
 @ c1d77557:bf04ec8b
2025-05-24 05:01:44
@ c1d77557:bf04ec8b
2025-05-24 05:01:44O P11Bet é uma plataforma inovadora que chega para oferecer uma experiência de jogo única, reunindo uma variedade de opções para os entusiastas de diferentes tipos de entretenimento online. Com uma interface moderna e fácil de usar, ela se destaca por proporcionar uma jornada divertida e segura para os jogadores, com um foco especial na qualidade da experiência e no atendimento às necessidades do público.
Uma Plataforma Completa e Acessível Ao acessar o P11Bet, os usuários encontram uma plataforma intuitiva, que facilita a navegação e oferece uma variedade de recursos para tornar o jogo mais agradável. A estrutura do site é otimizada para fornecer uma experiência fluida, seja no desktop ou em dispositivos móveis. Além disso, a plataforma se preocupa em manter um ambiente seguro, garantindo a proteção dos dados dos jogadores e permitindo que se concentrem na diversão.
A plataforma é projetada para todos os tipos de jogadores, desde os iniciantes até os mais experientes. A simplicidade de uso é uma das grandes vantagens, permitindo que qualquer pessoa possa se registrar e começar a jogar sem dificuldades. Além disso, a p11betoferece suporte ao cliente em português, o que facilita a comunicação e garante um atendimento de alta qualidade para os usuários brasileiros.
Diversidade de Jogos para Todos os Gostos O P11Bet se destaca pela vasta gama de opções de jogos que oferece aos seus usuários. A plataforma abriga uma seleção diversificada que vai desde jogos clássicos até as opções mais modernas, atendendo a todos os estilos e preferências. Entre as opções mais procuradas estão jogos de mesa, apostas esportivas, slots, e outras modalidades que garantem horas de entretenimento.
Um dos principais atrativos do P11Bet são os jogos de habilidade e de sorte, que exigem tanto estratégia quanto um pouco de sorte. As opções variam desde os mais simples aos mais complexos, oferecendo algo para todos os gostos. Os jogadores podem se aventurar em diversas modalidades, testando suas habilidades em jogos que vão de roletas e blackjack a versões mais inovadoras e dinâmicas.
Para aqueles que preferem algo mais emocionante e competitivo, as apostas esportivas são uma das maiores atrações. O P11Bet oferece uma ampla variedade de eventos esportivos ao vivo para apostar, com odds atrativas e uma plataforma que permite realizar apostas de forma rápida e eficiente. Seja em esportes populares como futebol, basquete ou até mesmo esportes menos tradicionais, há sempre algo para os apostadores mais exigentes.
A Experiência do Jogador: Diversão e Segurança O P11Bet não apenas se preocupa com a diversidade de jogos, mas também com a experiência do jogador. A plataforma foi desenvolvida para garantir que os jogadores possam desfrutar de seus jogos favoritos com a maior segurança e conforto possível. Além de um design intuitivo, a plataforma oferece diversas opções de pagamento, incluindo métodos populares no Brasil, para facilitar depósitos e retiradas. Isso garante que o processo de transações seja simples, rápido e seguro.
Outro ponto positivo do P11Bet é a experiência imersiva que ele oferece aos jogadores. A plataforma está sempre atualizada com novas funcionalidades, com promoções atraentes e bônus especiais que aumentam ainda mais a diversão. A interação com outros jogadores também é um diferencial, com espaços que permitem competir, conversar e trocar experiências com pessoas de todo o mundo.
Além disso, o suporte ao cliente da P11Bet é um dos mais elogiados pelos usuários. A equipe está sempre disponível para resolver dúvidas e fornecer assistência de maneira eficaz e amigável. Isso garante que os jogadores tenham sempre uma experiência tranquila, sem se preocupar com questões técnicas ou problemas relacionados à plataforma.
Conclusão Em resumo, o P11Bet é uma excelente escolha para quem busca uma plataforma completa e de qualidade para se divertir e desafiar suas habilidades. Com uma grande variedade de jogos, uma interface de fácil navegação e um suporte excepcional, ele garante que cada momento na plataforma seja único e prazeroso. Para quem deseja se aventurar no mundo dos jogos online, o P11Bet é uma opção que combina segurança, inovação e diversão.
-
 @ c1d77557:bf04ec8b
2025-05-24 05:01:11
@ c1d77557:bf04ec8b
2025-05-24 05:01:11Se você está em busca de uma experiência de jogo dinâmica e diversificada, o 59h é a plataforma que você precisa conhecer. Com um foco claro na satisfação dos jogadores, ela oferece uma ampla variedade de opções de entretenimento, além de uma interface amigável e segura. Neste artigo, vamos explorar a plataforma 59h, destacando suas principais funcionalidades, jogos emocionantes e a experiência do usuário.
O Que é a Plataforma 59h? O 59h é uma plataforma inovadora que oferece uma vasta gama de jogos e experiências digitais para os entusiastas do entretenimento online. A plataforma se destaca pela sua interface intuitiva, que permite aos jogadores navegar com facilidade entre as diferentes categorias de jogos. Ela é ideal para quem busca uma experiência divertida e acessível, sem complicações.
Desde o momento em que você acessa o 59h, fica evidente o compromisso com a qualidade. A plataforma é projetada para ser acessível em diversos dispositivos, seja no seu computador, tablet ou smartphone. Isso garante que os jogadores possam aproveitar seus jogos favoritos a qualquer momento e em qualquer lugar, com a mesma qualidade e desempenho.
Uma Grande Variedade de Jogos para Todos os Gostos O 59h se destaca por sua impressionante variedade de jogos. Independentemente do tipo de jogo que você prefere, certamente encontrará algo que se adapte ao seu estilo. A plataforma oferece desde jogos de habilidade, até opções mais relaxantes e divertidas para aqueles que buscam algo mais descontraído.
Entre as opções mais populares, destacam-se os jogos de mesa, onde os jogadores podem testar suas habilidades em jogos como pôquer, blackjack e outros. Para quem prefere algo mais voltado para a sorte, o 59h também oferece jogos com elementos de sorte que podem garantir grandes recompensas.
Além disso, a plataforma está sempre atualizando seu portfólio de jogos, trazendo novidades para os jogadores. Isso significa que você nunca ficará entediado, já que sempre haverá algo novo e emocionante para experimentar.
A Experiência do Jogador no 59h Uma das maiores qualidades da plataforma 59h é sua atenção à experiência do usuário. Desde o processo de registro até a escolha de um jogo, tudo foi pensado para garantir uma navegação tranquila e sem estresse.
A plataforma é completamente segura, oferecendo métodos de pagamento rápidos e confiáveis. Isso significa que os jogadores podem depositar e retirar seus fundos com confiança, sem se preocupar com a segurança de suas informações pessoais. Além disso, o suporte ao cliente está sempre disponível para ajudar em caso de dúvidas ou problemas, garantindo que sua experiência seja o mais fluida possível.
Outro ponto que merece destaque é a comunidade de jogadores. A interação com outros jogadores é uma parte importante da plataforma, permitindo que você compartilhe dicas, participe de torneios e crie amizades. A plataforma 59h se esforça para criar um ambiente amigável e inclusivo, onde todos podem se divertir e aprender uns com os outros.
Acessibilidade e Facilidade de Uso O 59h não é apenas sobre a diversidade de jogos; também se trata de tornar o acesso o mais simples possível. A plataforma oferece um design responsivo, que se adapta perfeitamente a qualquer tipo de dispositivo. Isso significa que você pode jogar no computador, smartphone ou tablet com a mesma facilidade.
O processo de cadastro é simples e rápido, permitindo que você comece a jogar em questão de minutos. Além disso, a plataforma oferece uma série de recursos adicionais, como promoções e bônus exclusivos, que tornam a experiência ainda mais empolgante.
Conclusão O 59h se posiciona como uma plataforma de entretenimento online completa, oferecendo uma vasta gama de jogos, uma experiência de usuário de alta qualidade e um ambiente seguro e amigável para jogadores de todos os níveis. Se você procura uma plataforma confiável, diversificada e divertida, o 59h é a escolha ideal. Não importa se você é um iniciante ou um jogador experiente, há sempre algo novo para descobrir e aproveitar no 59h.
-
 @ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08
@ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08Tldr
- Nostr is an open and interoperable protocol
- You can integrate it with workflow automation tools to augment your experience
- n8n is a great low/no-code workflow automation tool which you can host yourself
- Nostrobots allows you to integrate Nostr into n8n
- In this blog I create some workflow automations for Nostr
- A simple form to delegate posting notes
- Push notifications for mentions on multiple accounts
- Push notifications for your favourite accounts when they post a note
- All workflows are provided as open source with MIT license for you to use
Inter-op All The Things
Nostr is a new open social protocol for the internet. This open nature exciting because of the opportunities for interoperability with other technologies. In Using NFC Cards with Nostr I explored the
nostr:URI to launch Nostr clients from a card tap.The interoperability of Nostr doesn't stop there. The internet has many super-powers, and Nostr is open to all of them. Simply, there's no one to stop it. There is no one in charge, there are no permissioned APIs, and there are no risks of being de-platformed. If you can imagine technologies that would work well with Nostr, then any and all of them can ride on or alongside Nostr rails.
My mental model for why this is special is Google Wave ~2010. Google Wave was to be the next big platform. Lars was running it and had a big track record from Maps. I was excited for it. Then, Google pulled the plug. And, immediately all the time and capital invested in understanding and building on the platform was wasted.
This cannot happen to Nostr, as there is no one to pull the plug, and maybe even no plug to pull.
So long as users demand Nostr, Nostr will exist, and that is a pretty strong guarantee. It makes it worthwhile to invest in bringing Nostr into our other applications.
All we need are simple ways to plug things together.
Nostr and Workflow Automation
Workflow automation is about helping people to streamline their work. As a user, the most common way I achieve this is by connecting disparate systems together. By setting up one system to trigger another or to move data between systems, I can solve for many different problems and become way more effective.
n8n for workflow automation
Many workflow automation tools exist. My favourite is n8n. n8n is a low/no-code workflow automation platform which allows you to build all kinds of workflows. You can use it for free, you can self-host it, it has a user-friendly UI and useful API. Vs Zapier it can be far more elaborate. Vs Make.com I find it to be more intuitive in how it abstracts away the right parts of the code, but still allows you to code when you need to.
Most importantly you can plug anything into n8n: You have built-in nodes for specific applications. HTTP nodes for any other API-based service. And community nodes built by individual community members for any other purpose you can imagine.
Eating my own dogfood
It's very clear to me that there is a big design space here just demanding to be explored. If you could integrate Nostr with anything, what would you do?
In my view the best way for anyone to start anything is by solving their own problem first (aka "scratching your own itch" and "eating your own dogfood"). As I get deeper into Nostr I find myself controlling multiple Npubs – to date I have a personal Npub, a brand Npub for a community I am helping, an AI assistant Npub, and various testing Npubs. I need ways to delegate access to those Npubs without handing over the keys, ways to know if they're mentioned, and ways to know if they're posting.
I can build workflows with n8n to solve these issues for myself to start with, and keep expanding from there as new needs come up.
Running n8n with Nostrobots
I am mostly non-technical with a very helpful AI. To set up n8n to work with Nostr and operate these workflows should be possible for anyone with basic technology skills.
- I have a cheap VPS which currently runs my HAVEN Nostr Relay and Albyhub Lightning Node in Docker containers,
- My objective was to set up n8n to run alongside these in a separate Docker container on the same server, install the required nodes, and then build and host my workflows.
Installing n8n
Self-hosting n8n could not be easier. I followed n8n's Docker-Compose installation docs–
- Install Docker and Docker-Compose if you haven't already,
- Create your
docker-compose.ymland.envfiles from the docs, - Create your data folder
sudo docker volume create n8n_data, - Start your container with
sudo docker compose up -d, - Your n8n instance should be online at port
5678.
n8n is free to self-host but does require a license. Enter your credentials into n8n to get your free license key. You should now have access to the Workflow dashboard and can create and host any kind of workflows from there.
Installing Nostrobots
To integrate n8n nicely with Nostr, I used the Nostrobots community node by Ocknamo.
In n8n parlance a "node" enables certain functionality as a step in a workflow e.g. a "set" node sets a variable, a "send email" node sends an email. n8n comes with all kinds of "official" nodes installed by default, and Nostr is not amongst them. However, n8n also comes with a framework for community members to create their own "community" nodes, which is where Nostrobots comes in.
You can only use a community node in a self-hosted n8n instance (which is what you have if you are running in Docker on your own server, but this limitation does prevent you from using n8n's own hosted alternative).
To install a community node, see n8n community node docs. From your workflow dashboard–
- Click the "..." in the bottom left corner beside your username, and click "settings",
- Cilck "community nodes" left sidebar,
- Click "Install",
- Enter the "npm Package Name" which is
n8n-nodes-nostrobots, - Accept the risks and click "Install",
- Nostrobots is now added to your n8n instance.
Using Nostrobots
Nostrobots gives you nodes to help you build Nostr-integrated workflows–
- Nostr Write – for posting Notes to the Nostr network,
- Nostr Read – for reading Notes from the Nostr network, and
- Nostr Utils – for performing certain conversions you may need (e.g. from bech32 to hex).
Nostrobots has good documentation on each node which focuses on simple use cases.
Each node has a "convenience mode" by default. For example, the "Read" Node by default will fetch Kind 1 notes by a simple filter, in Nostrobots parlance a "Strategy". For example, with Strategy set to "Mention" the node will accept a pubkey and fetch all Kind 1 notes that Mention the pubkey within a time period. This is very good for quick use.
What wasn't clear to me initially (until Ocknamo helped me out) is that advanced use cases are also possible.
Each node also has an advanced mode. For example, the "Read" Node can have "Strategy" set to "RawFilter(advanced)". Now the node will accept json (anything you like that complies with NIP-01). You can use this to query Notes (Kind 1) as above, and also Profiles (Kind 0), Follow Lists (Kind 3), Reactions (Kind 7), Zaps (Kind 9734/9735), and anything else you can think of.
Creating and adding workflows
With n8n and Nostrobots installed, you can now create or add any kind of Nostr Workflow Automation.
- Click "Add workflow" to go to the workflow builder screen,
- If you would like to build your own workflow, you can start with adding any node. Click "+" and see what is available. Type "Nostr" to explore the Nostrobots nodes you have added,
- If you would like to add workflows that someone else has built, click "..." in the top right. Then click "import from URL" and paste in the URL of any workflow you would like to use (including the ones I share later in this article).
Nostr Workflow Automations
It's time to build some things!
A simple form to post a note to Nostr
I started very simply. I needed to delegate the ability to post to Npubs that I own in order that a (future) team can test things for me. I don't want to worry about managing or training those people on how to use keys, and I want to revoke access easily.
I needed a basic form with credentials that posted a Note.
For this I can use a very simple workflow–
- A n8n Form node – Creates a form for users to enter the note they wish to post. Allows for the form to be protected by a username and password. This node is the workflow "trigger" so that the workflow runs each time the form is submitted.
- A Set node – Allows me to set some variables, in this case I set the relays that I intend to use. I typically add a Set node immediately following the trigger node, and put all the variables I need in this. It helps to make the workflows easier to update and maintain.
- A Nostr Write node (from Nostrobots) – Writes a Kind-1 note to the Nostr network. It accepts Nostr credentials, the output of the Form node, and the relays from the Set node, and posts the Note to those relays.
Once the workflow is built, you can test it with the testing form URL, and set it to "Active" to use the production form URL. That's it. You can now give posting access to anyone for any Npub. To revoke access, simply change the credentials or set to workflow to "Inactive".
It may also be the world's simplest Nostr client.
You can find the Nostr Form to Post a Note workflow here.
Push notifications on mentions and new notes
One of the things Nostr is not very good at is push notifications. Furthermore I have some unique itches to scratch. I want–
- To make sure I never miss a note addressed to any of my Npubs – For this I want a push notification any time any Nostr user mentions any of my Npubs,
- To make sure I always see all notes from key accounts – For this I need a push notification any time any of my Npubs post any Notes to the network,
- To get these notifications on all of my devices – Not just my phone where my Nostr regular client lives, but also on each of my laptops to suit wherever I am working that day.
I needed to build a Nostr push notifications solution.
To build this workflow I had to string a few ideas together–
- Triggering the node on a schedule – Nostrobots does not include a trigger node. As every workflow starts with a trigger we needed a different method. I elected to run the workflow on a schedule of every 10-minutes. Frequent enough to see Notes while they are hot, but infrequent enough to not burden public relays or get rate-limited,
- Storing a list of Npubs in a Nostr list – I needed a way to store the list of Npubs that trigger my notifications. I initially used an array defined in the workflow, this worked fine. Then I decided to try Nostr lists (NIP-51, kind 30000). By defining my list of Npubs as a list published to Nostr I can control my list from within a Nostr client (e.g. Listr.lol or Nostrudel.ninja). Not only does this "just work", but because it's based on Nostr lists automagically Amethyst client allows me to browse that list as a Feed, and everyone I add gets notified in their Mentions,
- Using specific relays – I needed to query the right relays, including my own HAVEN relay inbox for notes addressed to me, and wss://purplepag.es for Nostr profile metadata,
- Querying Nostr events (with Nostrobots) – I needed to make use of many different Nostr queries and use quite a wide range of what Nostrobots can do–
- I read the EventID of my Kind 30000 list, to return the desired pubkeys,
- For notifications on mentions, I read all Kind 1 notes that mention that pubkey,
- For notifications on new notes, I read all Kind 1 notes published by that pubkey,
- Where there are notes, I read the Kind 0 profile metadata event of that pubkey to get the displayName of the relevant Npub,
- I transform the EventID into a Nevent to help clients find it.
- Using the Nostr URI – As I did with my NFC card article, I created a link with the
nostr:URI prefix so that my phone's native client opens the link by default, - Push notifications solution – I needed a push notifications solution. I found many with n8n integrations and chose to go with Pushover which supports all my devices, has a free trial, and is unfairly cheap with a $5-per-device perpetual license.
Once the workflow was built, lists published, and Pushover installed on my phone, I was fully set up with push notifications on Nostr. I have used these workflows for several weeks now and made various tweaks as I went. They are feeling robust and I'd welcome you to give them a go.
You can find the Nostr Push Notification If Mentioned here and If Posts a Note here.
In speaking with other Nostr users while I was building this, there are all kind of other needs for push notifications too – like on replies to a certain bookmarked note, or when a followed Npub starts streaming on zap.stream. These are all possible.
Use my workflows
I have open sourced all my workflows at my Github with MIT license and tried to write complete docs, so that you can import them into your n8n and configure them for your own use.
To import any of my workflows–
- Click on the workflow of your choice, e.g. "Nostr_Push_Notify_If_Mentioned.json",
- Click on the "raw" button to view the raw JSON, ex any Github page layout,
- Copy that URL,
- Enter that URL in the "import from URL" dialog mentioned above.
To configure them–
- Prerequisites, credentials, and variables are all stated,
- In general any variables required are entered into a Set Node that follows the trigger node,
- Pushover has some extra setup but is very straightforward and documented in the workflow.
What next?
Over my first four blogs I explored creating a good Nostr setup with Vanity Npub, Lightning Payments, Nostr Addresses at Your Domain, and Personal Nostr Relay.
Then in my latest two blogs I explored different types of interoperability with NFC cards and now n8n Workflow Automation.
Thinking ahead n8n can power any kind of interoperability between Nostr and any other legacy technology solution. On my mind as I write this:
- Further enhancements to posting and delegating solutions and forms (enhanced UI or different note kinds),
- Automated or scheduled posting (such as auto-liking everything Lyn Alden posts),
- Further enhancements to push notifications, on new and different types of events (such as notifying me when I get a new follower, on replies to certain posts, or when a user starts streaming),
- All kinds of bridges, such as bridging notes to and from Telegram, Slack, or Campfire. Or bridging RSS or other event feeds to Nostr,
- All kinds of other automation (such as BlackCoffee controlling a coffee machine),
- All kinds of AI Assistants and Agents,
In fact I have already released an open source workflow for an AI Assistant, and will share more about that in my next blog.
Please be sure to let me know if you think there's another Nostr topic you'd like to see me tackle.
GM Nostr.
-
 @ 2b998b04:86727e47
2025-05-25 03:19:19
@ 2b998b04:86727e47
2025-05-25 03:19:19n an inflationary system, the goal is often just to keep up.
With prices always rising, most of us are stuck in a race:\ Earn more to afford more.\ Spend before your money loses value.\ Monetize everything just to stay ahead of the curve.
Work becomes reactive.\ You hustle to outrun rising costs.\ You take on projects you don’t believe in just to make next month’s bills.\ Money decays. So you move faster, invest riskier, and burn out quicker.
But what happens when the curve flips?
A deflationary economy—like the one Bitcoin makes possible—rewards stillness, reflection, and intentionality.
Time favors the saver, not the spender.\ Money gains purchasing power.\ You’re no longer punished for patience.
You don’t have to convert your energy into cash before it loses value.\ You don’t have to be always on.\ You can actually afford to wait for the right work.
And when you do work—it means more.
💡 The “bullshit jobs” David Graeber wrote about start to disappear.\ There’s no need to look busy just to justify your existence.\ There’s no reward for parasitic middle layers.\ Instead, value flows to real craft, real care, and real proof of work—philosophically and literally.
So what does a job look like in that world?
— A farmer building soil instead of chasing subsidies.\ — An engineer optimizing for simplicity instead of speed.\ — A craftsman making one perfect table instead of ten cheap ones.\ — A writer telling the truth without clickbait.\ — A builder who says no more than they say yes.
You choose work that endures—not because it pays instantly, but because it’s worth doing.
The deflationary future isn’t a fantasy.\ It’s a recalibration.
It’s not about working less.\ It’s about working better.
That’s what Bitcoin taught me.\ That’s what I’m trying to live now.
🟠 If you’re trying to align your work with these values, I’d love to connect.\ Zap this post, reply with your story, or follow along as I build—without permission, but with conviction.\ [https://tinyurl.com/yuyu2b9t](https://tinyurl.com/yuyu2b9t)