-
 @ bd32f268:22b33966
2024-10-24 17:57:26
@ bd32f268:22b33966
2024-10-24 17:57:26A atualidade acostumou-nos a uma lânguida linguagem devido à cultura do politicamente correto e ao crescente relativismo em que vivemos. A confusão é tanta que já não se chamam os bois pelos nomes e este ambiente faz com que inclusive desconheçamos o significado das palavras. A este respeito temos visto cada vez mais indefinição sobre o que são os vícios e sobre o que são as virtudes. Tal é a confusão que por vezes trocamos o significado de uns pelos outros.
A coragem e a convicção facilmente passam por orgulho e arrogância, a castidade passa por beatice e por aí segue a confusão com muitos outros termos.
A inversão de valores é tão disseminada que atrocidades como a pornografia, o aborto, o adultério entre outras atrocidades são celebrados como conquistas civilizacionais. A sua disseminação é de tal forma que hoje a pessoa média já banalizou e normalizou completamente estes aspectos.
“Primeiro estranha-se depois entranha-se.”
Fernando Pessoa
Enquanto isto acontece por um lado, por outro a defesa da família, da identidade e da tradição são abertamente atacadas como se se tratassem de produtos de uma cultura opressora que deve ser combatida por todos os meios. Por agora a perseguição destas ideias é ainda maioritariamente realizada através da exclusão social e económica, no entanto, não são escassos os exemplos da história em que essa perseguição assume uma outra dimensão.
Desta forma, está criado um paradigma e um sistema de incentivos que premeia a pessoa que colabora com o sistema vigente. Tanto é assim que se multiplicam cada vez mais os exemplos de programas de quotas e subvenções que permitem, a quem possui um grau mais avançado de assimilação ideológica progredir socialmente atalhando o caminho para o fazer.
“Assim, toda a árvore boa produz bons frutos, porém a árvore má produz frutos maus. Não pode a árvore boa produzir frutos maus, nem a árvore má produzir frutos bons (…)”
Mateus 7:17-18“Assim, toda a árvore boa produz bons frutos, porém a árvore má produz frutos maus. Não pode a árvore boa produzir frutos maus, nem a árvore má produzir frutos bons (…)”
> Mateus 7:17-18*
Desengane-se quem pensa que no paradigma pos-moderno não há moralização, sacerdotes e uma matriz religiosa, tudo isso existe.
Os psicólogos, para mal da nossa sociedade, são crescentemente os sacerdotes desta religião pagã, aquela que baseada numa filosofia e antropologia erradas vai corrompendo intelecto e coração.
Nesta nova ordem social, que em abono da verdade é já antiga, a inversão de valores é tal que já a própria vida humana é sacrificada no altar do clima em abono da “mãe” natureza. Regredimos ao tribalismo que nos sugere que a natureza vale mais que a vida humana.
Este é apenas um exemplo dos rituais de sacrifício proporcionados pela “nova” religião. Um outro exemplo que podemos dar é o da castração química e física de crianças e jovens no altar da falsa compaixão e empatia. Ainda um outro exemplo que podemos dar é o da promoção do homossexualismo, do transexualismo e da não-monogamia como caminhos saudáveis a seguir, sacrificando a vida de muitos jovens confusos no altar da inclusão. Muitos mais exemplos poderiam ser dados, porque à medida que esta “nova” religião aumenta a sua ortodoxia os rituais vão ficando cada vez mais assombrosos.
Estes rituais têm por base uma apologia ao anti logos, quer isto dizer que procuram negar tudo o que é conhecimento básico sobre a realidade e sobre a verdade. A própria razão e lógica não se sustentam quando vemos situações como a de homens a competir em desportos femininos. As leis desta nova ordem são: “procura a felicidade (aqui muitas vezes entendida como o prazer) como fim último da vida “; “todas as opiniões são certas e não há uma verdade”; “Não servirás a nenhuma autoridade”; “não seguir o vício é opressão e seguir o vício é liberdade”.
Neste ambiente inóspito, quem quiser preservar a honra e a virtude terá cada vez mais dificuldade uma vez que a dissidência desta nova religião não é aplaudida, pelo contrário é anatematizada. Porém, importa dizer que independentemente da época há sempre espaço para o heroísmo e para a transformação destas dificuldades em degraus para que o indivíduo se possa distinguir dos demais pelas suas virtudes. Onde o vício abunda também maior o destaque será em relação à graça, como uma pedra preciosa reluzente no meio da lama que aparenta brilhar mais intensamente aos nossos olhos tal é o contraste, ou como uma luz na escuridão que se distingue facilmente.
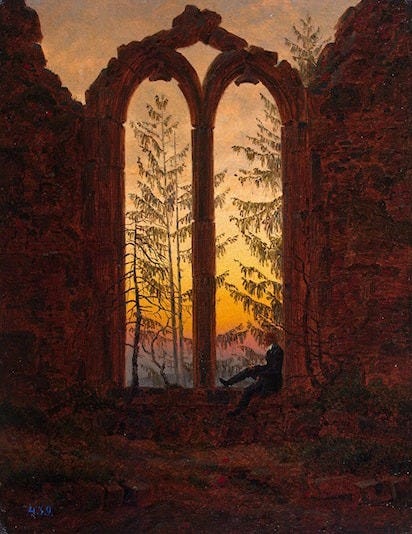 ###### Casper David Friedrich - dreaming man in church ruins
###### Casper David Friedrich - dreaming man in church ruins -
 @ 32e18276:5c68e245
2023-12-06 15:29:43
@ 32e18276:5c68e245
2023-12-06 15:29:43I’m going to be on an ordinals panels as one of the people who is counter arguing the claim that they are good for bitcoin. I decided to brush up on the technicals on how inscriptions work. I am starting to see luke’s perspective on how it is exploiting a loophole in bitcoin’s anti-data-spam mechanisms.
Storing data in Bitcoin, the “standard” way
The standard way you add “data” to bitcoin is by calling the OP_RETURN opcode. Bitcoin devs noticed that people were storing data (like the bitcoin whitepaper) in the utxo set via large multisig transactions. The problem with this is that this set is unprunable and could grow over time. OP_RETURN outputs on the other-hand are provably prunable and don’t add to utxo bloat.
Here’s an excerpt from the march 2014 0.9.0 release notes that talks about this:
On OP_RETURN: There was been some confusion and misunderstanding in the community, regarding the OP_RETURN feature in 0.9 and data in the blockchain. This change is not an endorsement of storing data in the blockchain. The OP_RETURN change creates a provably-prunable output, to avoid data storage schemes – some of which were already deployed – that were storing arbitrary data such as images as forever-unspendable TX outputs, bloating bitcoin’s UTXO database. Storing arbitrary data in the blockchain is still a bad idea; it is less costly and far more efficient to store non-currency data elsewhere.
Much of the work on bitcoin core has been focused on making sure the system continues to function in a decentralized way for its intended purpose in the presence of people trying to abuse it for things like storing data. Bitcoin core has always discouraged this, as it is not designed for storage of images and data, it is meant for moving digital coins around in cyberspace.
To help incentive-align people to not do stupid things, OP_RETURN transactions were not made non-standard, so that they are relayable by peers and miners, but with the caveat:
- They can only push 40 bytes (later increased to 80,83, I’m guessing to support larger root merkle hashes since that is the only sane usecase for op_return)
Bitcoin also added an option called -datacarriersize which limits the total number of bytes from these outputs that you will relay or mine.
Why inscriptions are technically an exploit
Inscriptions get around the datacarriersize limit by disguising data as bitcoin script program data via OP_PUSH inside OP_IF blocks. Ordinals do not use OP_RETURN and are not subjected to datacarriersize limits, so noderunners and miners currently have limited control over the total size of this data that they wish to relay and include in blocks. Luke’s fork of bitcoin-core has some options to fight this spam, so hopefully we will see this in core sometime soon as well.
Inscriptions are also taking advantage of features in segwit v1 (witness discount) and v2/taproot (no arbitrary script size limit). Each of these features have interesting and well-justified reasons why they were introduced.
The purpose of the witness discount was to make it cheaper to spend many outputs which helps the reduction of the utxo set size. Inscriptions took advantage of this discount to store monke jpegs disguised as bitcoin scripts. Remember, bitcoin is not for storing data, so anytime bitcoin-devs accidentally make it cheap and easy to relay data then this should be viewed as an exploit. Expect it to be fixed, or at least provide tools to noderunners for fighting this spam.
Where do we go from here
The interesting part of this story is that people seem to attach value to images stored on the bitcoin blockchain, and they are willing to pay the fee to get it in the block, so non-ideologic miners and people who don’t care about the health and decentralization of bitcoin are happy to pay or collect the fee and move on.
Data should not get a discount, people should pay full price if they want to store data. They should just use op_return and hashes like opentimestamps or any other reasonable protocol storing data in bitcoin.
After going through this analysis I’ve come to the opinion that this is a pretty bad data-spam exploit and bitcoin devs should be working on solutions. Ideological devs like luke who actually care about the health and decentralization of the network are and I’m glad to see it.
-
 @ 8947a945:9bfcf626
2024-10-17 08:06:55
@ 8947a945:9bfcf626
2024-10-17 08:06:55สวัสดีทุกคนบน Nostr ครับ รวมไปถึง watchersและ ผู้ติดตามของผมจาก Deviantart และ platform งานศิลปะอื่นๆนะครับ
ตั้งแต่ต้นปี 2024 ผมใช้ AI เจนรูปงานตัวละครสาวๆจากอนิเมะ และเปิด exclusive content ให้สำหรับผู้ที่ชื่นชอบผลงานของผมเป็นพิเศษ
ผมโพสผลงานผมทั้งหมดไว้ที่เวบ Deviantart และค่อยๆสร้างฐานผู้ติดตามมาเรื่อยๆอย่างค่อยเป็นค่อยไปมาตลอดครับ ทุกอย่างเติบโตไปเรื่อยๆของมัน ส่วนตัวผมมองว่ามันเป็นพิร์ตธุรกิจออนไลน์ ของผมพอร์ตนึงได้เลย
เมื่อวันที่ 16 กย.2024 มีผู้ติดตามคนหนึ่งส่งข้อความส่วนตัวมาหาผม บอกว่าชื่นชอบผลงานของผมมาก ต้องการจะขอซื้อผลงาน แต่ขอซื้อเป็น NFT นะ เสนอราคาซื้อขายต่อชิ้นที่สูงมาก หลังจากนั้นผมกับผู้ซื้อคนนี้พูดคุยกันในเมล์ครับ
นี่คือข้อสรุปสั่นๆจากการต่อรองซื้อขายครับ
(หลังจากนี้ผมขอเรียกผู้ซื้อว่า scammer นะครับ เพราะไพ่มันหงายมาแล้ว ว่าเขาคือมิจฉาชีพ)

- Scammer รายแรก เลือกผลงานที่จะซื้อ เสนอราคาซื้อที่สูงมาก แต่ต้องเป็นเวบไซต์ NFTmarket place ที่เขากำหนดเท่านั้น มันทำงานอยู่บน ERC20 ผมเข้าไปดูเวบไซต์ที่ว่านี้แล้วรู้สึกว่ามันดูแปลกๆครับ คนที่จะลงขายผลงานจะต้องใช้ email ในการสมัครบัญชีซะก่อน ถึงจะผูก wallet อย่างเช่น metamask ได้ เมื่อผูก wallet แล้วไม่สามารถเปลี่ยนได้ด้วย ตอนนั้นผมใช้ wallet ที่ไม่ได้ link กับ HW wallet ไว้ ทดลองสลับ wallet ไปๆมาๆ มันทำไม่ได้ แถมลอง log out แล้ว เลข wallet ก็ยังคาอยู่อันเดิม อันนี้มันดูแปลกๆแล้วหนึ่งอย่าง เวบนี้ค่า ETH ในการ mint 0.15 - 0.2 ETH … ตีเป็นเงินบาทนี่แพงบรรลัยอยู่นะครับ

-
Scammer รายแรกพยายามชักจูงผม หว่านล้อมผมว่า แหม เดี๋ยวเขาก็มารับซื้องานผมน่า mint งานเสร็จ รีบบอกเขานะ เดี๋ยวเขารีบกดซื้อเลย พอขายได้กำไร ผมก็ได้ค่า gas คืนได้ แถมยังได้กำไรอีก ไม่มีอะไรต้องเสีนจริงมั้ย แต่มันเป้นความโชคดีครับ เพราะตอนนั้นผมไม่เหลือทุนสำรองที่จะมาซื้อ ETH ได้ ผมเลยต่อรองกับเขาตามนี้ครับ :
-
ผมเสนอว่า เอางี้มั้ย ผมส่งผลงานของผมแบบ low resolution ให้ก่อน แลกกับให้เขาช่วยโอน ETH ที่เป็นค่า mint งานมาให้หน่อย พอผมได้ ETH แล้ว ผมจะ upscale งานของผม แล้วเมล์ไปให้ ใจแลกใจกันไปเลย ... เขาไม่เอา
- ผมเสนอให้ไปซื้อที่ร้านค้าออนไลน์ buymeacoffee ของผมมั้ย จ่ายเป็น USD ... เขาไม่เอา
- ผมเสนอให้ซื้อขายผ่าน PPV lightning invoice ที่ผมมีสิทธิ์เข้าถึง เพราะเป็น creator ของ Creatr ... เขาไม่เอา
- ผมยอกเขาว่างั้นก็รอนะ รอเงินเดือนออก เขาบอก ok
สัปดาห์ถัดมา มี scammer คนที่สองติดต่อผมเข้ามา ใช้วิธีการใกล้เคียงกัน แต่ใช้คนละเวบ แถมเสนอราคาซื้อที่สูงกว่าคนแรกมาก เวบที่สองนี้เลวร้ายค่าเวบแรกอีกครับ คือต้องใช้เมล์สมัครบัญชี ไม่สามารถผูก metamask ได้ พอสมัครเสร็จจะได้ wallet เปล่าๆมาหนึ่งอัน ผมต้องโอน ETH เข้าไปใน wallet นั้นก่อน เพื่อเอาไปเป็นค่า mint NFT 0.2 ETH
ผมบอก scammer รายที่สองว่า ต้องรอนะ เพราะตอนนี้กำลังติดต่อซื้อขายอยู่กับผู้ซื้อรายแรกอยู่ ผมกำลังรอเงินเพื่อมาซื้อ ETH เป็นต้นทุนดำเนินงานอยู่ คนคนนี้ขอให้ผมส่งเวบแรกไปให้เขาดูหน่อย หลังจากนั้นไม่นานเขาเตือนผมมาว่าเวบแรกมันคือ scam นะ ไม่สามารถถอนเงินออกมาได้ เขายังส่งรูป cap หน้าจอที่คุยกับผู้เสียหายจากเวบแรกมาให้ดูว่าเจอปัญหาถอนเงินไม่ได้ ไม่พอ เขายังบลัฟ opensea ด้วยว่าลูกค้าขายงานได้ แต่ถอนเงินไม่ได้
Opensea ถอนเงินไม่ได้ ตรงนี้แหละครับคือตัวกระตุกต่อมเอ๊ะของผมดังมาก เพราะ opensea อ่ะ ผู้ใช้ connect wallet เข้ากับ marketplace โดยตรง ซื้อขายกันเกิดขึ้น เงินวิ่งเข้าวิ่งออก wallet ของแต่ละคนโดยตรงเลย opensea เก็บแค่ค่า fee ในการใช้ platform ไม่เก็บเงินลูกค้าไว้ แถมปีนี้ค่า gas fee ก็ถูกกว่า bull run cycle 2020 มาก ตอนนี้ค่า gas fee ประมาณ 0.0001 ETH (แต่มันก็แพงกว่า BTC อยู่ดีอ่ะครับ)
ผมเลยเอาเรื่องนี้ไปปรึกษาพี่บิท แต่แอดมินมาคุยกับผมแทน ทางแอดมินแจ้งว่ายังไม่เคยมีเพื่อนๆมาปรึกษาเรื่องนี้ กรณีที่ผมทักมาถามนี่เป็นรายแรกเลย แต่แอดมินให้ความเห็นไปในทางเดียวกับสมมุติฐานของผมว่าน่าจะ scam ในเวลาเดียวกับผมเอาเรื่องนี้ไปถามในเพจ NFT community คนไทนด้วย ได้รับการ confirm ชัดเจนว่า scam และมีคนไม่น้อยโดนหลอก หลังจากที่ผมรู้ที่มาแล้ว ผมเลยเล่นสงครามปั่นประสาท scammer ทั้งสองคนนี้ครับ เพื่อดูว่าหลอกหลวงมิจฉาชีพจริงมั้ย
โดยวันที่ 30 กย. ผมเลยปั่นประสาน scammer ทั้งสองรายนี้ โดยการ mint ผลงานที่เขาเสนอซื้อนั่นแหละ ขึ้น opensea แล้วส่งข้อความไปบอกว่า
mint ให้แล้วนะ แต่เงินไม่พอจริงๆว่ะโทษที เลย mint ขึ้น opensea แทน พอดีบ้านจน ทำได้แค่นี้ไปถึงแค่ opensea รีบไปซื้อล่ะ มีคนจ้องจะคว้างานผมเยอะอยู่ ผมไม่คิด royalty fee ด้วยนะเฮ้ย เอาไปขายต่อไม่ต้องแบ่งกำไรกับผม
เท่านั้นแหละครับ สงครามจิตวิทยาก็เริ่มขึ้น แต่เขาจนมุม กลืนน้ำลายตัวเอง ช็อตเด็ดคือ
เขา : เนี่ยอุส่ารอ บอกเพื่อนในทีมว่าวันจันทร์ที่ 30 กย. ได้ของแน่ๆ เพื่อนๆในทีมเห็นงานผมแล้วมันสวยจริง เลยใส่เงินเต็มที่ 9.3ETH (+ capture screen ส่งตัวเลขยอดเงินมาให้ดู)ไว้รอโดยเฉพาะเลยนะ ผม : เหรอ ... งั้น ขอดู wallet address ที่มี transaction มาให้ดูหน่อยสิ เขา : 2ETH นี่มัน 5000$ เลยนะ ผม : แล้วไง ขอดู wallet address ที่มีการเอายอดเงิน 9.3ETH มาให้ดูหน่อย ไหนบอกว่าเตรียมเงินไว้มากแล้วนี่ ขอดูหน่อย ว่าใส่ไว้เมื่อไหร่ ... เอามาแค่ adrress นะเว้ย ไม่ต้องทะลึ่งส่ง seed มาให้ เขา : ส่งรูปเดิม 9.3 ETH มาให้ดู ผม : รูป screenshot อ่ะ มันไม่มีความหมายหรอกเว้ย ตัดต่อเอาก็ได้ง่ายจะตาย เอา transaction hash มาดู ไหนว่าเตรียมเงินไว้รอ 9.3ETH แล้วอยากซื้องานผมจนตัวสั่นเลยไม่ใช่เหรอ ถ้าจะส่ง wallet address มาให้ดู หรือจะช่วยส่ง 0.15ETH มาให้ยืม mint งานก่อน แล้วมากดซื้อ 2ETH ไป แล้วผมใช้ 0.15ETH คืนให้ก็ได้ จะซื้อหรือไม่ซื้อเนี่ย เขา : จะเอา address เขาไปทำไม ผม : ตัดจบ รำคาญ ไม่ขายให้ละ เขา : 2ETH = 5000 USD เลยนะ ผม : แล้วไง
ผมเลยเขียนบทความนี้มาเตือนเพื่อนๆพี่ๆทุกคนครับ เผื่อใครกำลังเปิดพอร์ตทำธุรกิจขาย digital art online แล้วจะโชคดี เจอของดีแบบผม
ทำไมผมถึงมั่นใจว่ามันคือการหลอกหลวง แล้วคนโกงจะได้อะไร
อันดับแรกไปพิจารณาดู opensea ครับ เป็นเวบ NFTmarketplace ที่ volume การซื้อขายสูงที่สุด เขาไม่เก็บเงินของคนจะซื้อจะขายกันไว้กับตัวเอง เงินวิ่งเข้าวิ่งออก wallet ผู้ซื้อผู้ขายเลย ส่วนทางเวบเก็บค่าธรรมเนียมเท่านั้น แถมค่าธรรมเนียมก็ถูกกว่าเมื่อปี 2020 เยอะ ดังนั้นการที่จะไปลงขายงานบนเวบ NFT อื่นที่ค่า fee สูงกว่ากันเป็นร้อยเท่า ... จะทำไปทำไม
ผมเชื่อว่า scammer โกงเงินเจ้าของผลงานโดยการเล่นกับความโลภและความอ่อนประสบการณ์ของเจ้าของผลงานครับ เมื่อไหร่ก็ตามที่เจ้าของผลงานโอน ETH เข้าไปใน wallet เวบนั้นเมื่อไหร่ หรือเมื่อไหร่ก็ตามที่จ่ายค่า fee ในการ mint งาน เงินเหล่านั้นสิ่งเข้ากระเป๋า scammer ทันที แล้วก็จะมีการเล่นตุกติกต่อแน่นอนครับ เช่นถอนไม่ได้ หรือซื้อไม่ได้ ต้องโอนเงินมาเพิ่มเพื่อปลดล็อค smart contract อะไรก็ว่าไป แล้วคนนิสัยไม่ดีพวกเนี้ย ก็จะเล่นกับความโลภของคน เอาราคาเสนอซื้อที่สูงโคตรๆมาล่อ ... อันนี้ไม่ว่ากัน เพราะบนโลก NFT รูปภาพบางรูปที่ไม่ได้มีความเป็นศิลปะอะไรเลย มันดันขายกันได้ 100 - 150 ETH ศิลปินที่พยายามสร้างตัวก็อาจจะมองว่า ผลงานเรามีคนรับซื้อ 2 - 4 ETH ต่องานมันก็มากพอแล้ว (จริงๆมากเกินจนน่าตกใจด้วยซ้ำครับ)
บนโลกของ BTC ไม่ต้องเชื่อใจกัน โอนเงินไปหากันได้ ปิดสมุดบัญชีได้โดยไม่ต้องเชื่อใจกัน
บบโลกของ ETH "code is law" smart contract มีเขียนอยู่แล้ว ไปอ่าน มันไม่ได้ยากมากในการทำความเข้าใจ ดังนั้น การจะมาเชื่อคำสัญญาจากคนด้วยกัน เป็นอะไรที่ไม่มีเหตุผล
ผมไปเล่าเรื่องเหล่านี้ให้กับ community งานศิลปะ ก็มีทั้งเสียงตอบรับที่ดี และไม่ดีปนกันไป มีบางคนยืนยันเสียงแข็งไปในทำนองว่า ไอ้เรื่องแบบเนี้ยไม่ได้กินเขาหรอก เพราะเขาตั้งใจแน่วแน่ว่างานศิลป์ของเขา เขาไม่เอาเข้ามายุ่งในโลก digital currency เด็ดขาด ซึ่งผมก็เคารพมุมมองเขาครับ แต่มันจะดีกว่ามั้ย ถ้าเราเปิดหูเปิดตาให้ทันเทคโนโลยี โดยเฉพาะเรื่อง digital currency , blockchain โดนโกงทีนึงนี่คือหมดตัวกันง่ายกว่าเงิน fiat อีก
อยากจะมาเล่าให้ฟังครับ และอยากให้ช่วยแชร์ไปให้คนรู้จักด้วย จะได้ระวังตัวกัน
Note
- ภาพประกอบ cyber security ทั้งสองนี่ของผมเองครับ ทำเอง วางขายบน AdobeStock
- อีกบัญชีนึงของผม "HikariHarmony" npub1exdtszhpw3ep643p9z8pahkw8zw00xa9pesf0u4txyyfqvthwapqwh48sw กำลังค่อยๆเอาผลงานจากโลกข้างนอกเข้ามา nostr ครับ ตั้งใจจะมาสร้างงานศิลปะในนี้ เพื่อนๆที่ชอบงาน จะได้ไม่ต้องออกไปหาที่ไหน
ผลงานของผมครับ - Anime girl fanarts : HikariHarmony - HikariHarmony on Nostr - General art : KeshikiRakuen - KeshikiRakuen อาจจะเป็นบัญชี nostr ที่สามของผม ถ้าไหวครับ
-
 @ b83e6f82:73c27758
2024-10-25 14:19:14
@ b83e6f82:73c27758
2024-10-25 14:19:14Citrine 0.5.4
- Fix notification icon size
- Fix loading screen
- Update dependencies
Download it with zap.store, Obtainium, f-droid or download it directly in the releases page
If you like my work consider making a donation
Verifying the release
In order to verify the release, you'll need to have
gpgorgpg2installed on your system. Once you've obtained a copy (and hopefully verified that as well), you'll first need to import the keys that have signed this release if you haven't done so already:bash gpg --keyserver hkps://keys.openpgp.org --recv-keys 44F0AAEB77F373747E3D5444885822EED3A26A6DOnce you have his PGP key you can verify the release (assuming
manifest-v0.5.4.txtandmanifest-v0.5.4.txt.sigare in the current directory) with:bash gpg --verify manifest-v0.5.4.txt.sig manifest-v0.5.4.txtYou should see the following if the verification was successful:
bash gpg: Signature made Fri 13 Sep 2024 08:06:52 AM -03 gpg: using RSA key 44F0AAEB77F373747E3D5444885822EED3A26A6D gpg: Good signature from "greenart7c3 <greenart7c3@proton.me>"That will verify the signature on the main manifest page which ensures integrity and authenticity of the binaries you've downloaded locally. Next, depending on your operating system you should then re-calculate the sha256 sum of the binary, and compare that with the following hashes:
bash cat manifest-v0.5.4.txtOne can use the
shasum -a 256 <file name here>tool in order to re-compute thesha256hash of the target binary for your operating system. The produced hash should be compared with the hashes listed above and they should match exactly. -
 @ 4ba8e86d:89d32de4
2024-10-25 13:17:33
@ 4ba8e86d:89d32de4
2024-10-25 13:17:33Foi criado com o objetivo de fornecer aos usuários uma experiência de navegação mais privada e segura na internet. O LibreWolf é uma excelente alternativa ao Firefox, com algumas diferenças significativas em relação ao navegador da Mozilla.
O LibreWolf foi desenvolvido com foco na privacidade e segurança do usuário. Ele bloqueia rastreadores de terceiros, impede o envio de dados de telemetria e desabilita recursos de rastreamento de usuário que vêm ativados por padrão no Firefox. Além disso, ele vem pré-configurado com diversas extensões de privacidade, como uBlock Origin, Privacy Badger e HTTPS Everywhere, que ajudam a bloquear anúncios, scripts maliciosos e outras ameaças de segurança enquanto você navega na web.
Outra característica notável do LibreWolf é que ele usa o mecanismo de pesquisa Searx como padrão, em vez do Google. O Searx é conhecido por fornecer resultados de pesquisa mais privados e anônimos, sem rastrear as suas atividades online. O LibreWolf também possui suporte nativo ao Tor, que permite aos usuários acessar a internet anonimamente.
Além dos recursos de privacidade e segurança, o LibreWolf é muito semelhante ao Firefox em termos de usabilidade e funcionalidades. Ele é fácil de instalar e configurar, e possui um grande número de extensões disponíveis na sua loja de extensões.
O LibreWolf é uma excelente opção para usuários que buscam um navegador mais privado e seguro. Se você se preocupa com a sua privacidade online, vale a pena experimentar o LibreWolf. Ele é gratuito e de código aberto, o que significa que você pode baixá-lo e personalizá-lo de acordo com suas necessidades específicas.
https://librewolf.net/
https://github.com/librewolf-community
-
 @ 6bae33c8:607272e8
2024-10-25 12:50:49
@ 6bae33c8:607272e8
2024-10-25 12:50:49I went 4-1 last week which brings my two-week run to 8-2, though it’s not enough to salvage Q2 because I was 2-3 in Week 5. Even if I go 5-0 this week, that’s only 15-5, and that won’t cut it to get a share of the prize. But I’d like to keep it going if only to confirm that after a slow start I’m finally getting in sync.
My Picks
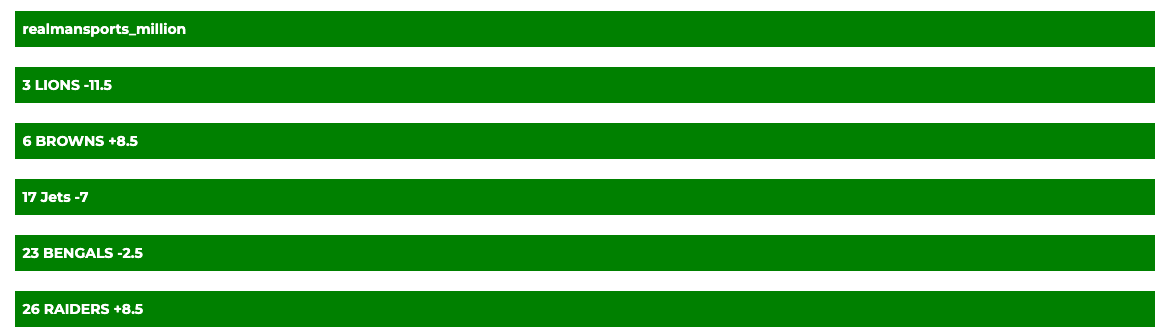
Lions -11.5 vs Titans — I rarely take double-digit favorites, but 11.5 seems low to me. In a normal year this would be 14 in Detroit.
Browns +8.5 vs Ravens — This is a big line on the road, and the Browns have to feel good putting the Deshaun Watson fiasco behind them. (Almost like a relaxing massage.) Might also be a look-ahead game after quality wins for the Ravens.
Jets -7 at Patriots — This line is too big, and Drake Maye might turn out to be a player. But this feels like a get-well spot for the Jets after some tough losses.
Bengals -2.5 vs Eagles — The Eagles are a good sell high off a big win against a weak Giants team. The Bengals are slow starters, but they’re starting to get going.
Raiders +8.5 vs Chiefs — This line is up to 9.5 in places, I knew that, but took the Raiders anyway. Just seems like a divisional game where the beaten-down dog shows up.
-
 @ 8947a945:9bfcf626
2024-10-17 07:33:00
@ 8947a945:9bfcf626
2024-10-17 07:33:00Hello everyone on Nostr and all my watchersand followersfrom DeviantArt, as well as those from other art platforms
I have been creating and sharing AI-generated anime girl fanart since the beginning of 2024 and have been running member-exclusive content on Patreon.
I also publish showcases of my artworks to Deviantart. I organically build up my audience from time to time. I consider it as one of my online businesses of art. Everything is slowly growing
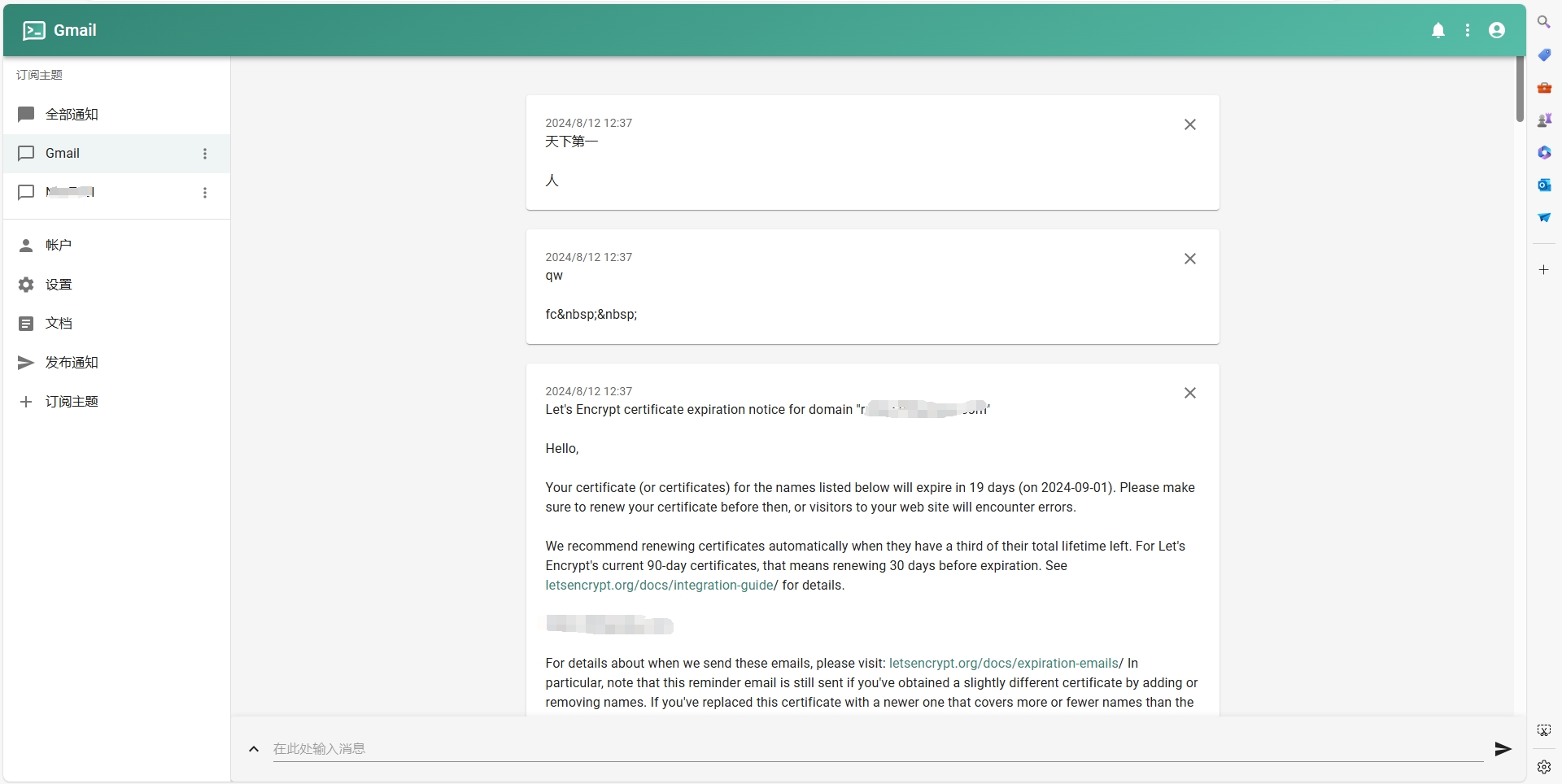
On September 16, I received a DM from someone expressing interest in purchasing my art in NFT format and offering a very high price for each piece. We later continued the conversation via email.
Here’s a brief overview of what happened

- The first scammer selected the art they wanted to buy and offered a high price for each piece. They provided a URL to an NFT marketplace site running on the Ethereum (ETH) mainnet or ERC20. The site appeared suspicious, requiring email sign-up and linking a MetaMask wallet. However, I couldn't change the wallet address later. The minting gas fees were quite expensive, ranging from 0.15 to 0.2 ETH

-
The scammers tried to convince me that the high profits would easily cover the minting gas fees, so I had nothing to lose. Luckily, I didn’t have spare funds to purchase ETH for the gas fees at the time, so I tried negotiating with them as follows:
-
I offered to send them a lower-quality version of my art via email in exchange for the minting gas fees, but they refused.
- I offered them the option to pay in USD through Buy Me a Coffee shop here, but they refused.
- I offered them the option to pay via Bitcoin using the Lightning Network invoice , but they refused.
- I asked them to wait until I could secure the funds, and they agreed to wait.
The following week, a second scammer approached me with a similar offer, this time at an even higher price and through a different NFT marketplace website.
This second site also required email registration, and after navigating to the dashboard, it asked for a minting fee of 0.2 ETH. However, the site provided a wallet address for me instead of connecting a MetaMask wallet.
I told the second scammer that I was waiting to make a profit from the first sale, and they asked me to show them the first marketplace. They then warned me that the first site was a scam and even sent screenshots of victims, including one from OpenSea saying that Opensea is not paying.
This raised a red flag, and I began suspecting I might be getting scammed. On OpenSea, funds go directly to users' wallets after transactions, and OpenSea charges a much lower platform fee compared to the previous crypto bull run in 2020. Minting fees on OpenSea are also significantly cheaper, around 0.0001 ETH per transaction.
I also consulted with Thai NFT artist communities and the ex-chairman of the Thai Digital Asset Association. According to them, no one had reported similar issues, but they agreed it seemed like a scam.
After confirming my suspicions with my own research and consulting with the Thai crypto community, I decided to test the scammers’ intentions by doing the following
I minted the artwork they were interested in, set the price they offered, and listed it for sale on OpenSea. I then messaged them, letting them know the art was available and ready to purchase, with no royalty fees if they wanted to resell it.
They became upset and angry, insisting I mint the art on their chosen platform, claiming they had already funded their wallet to support me. When I asked for proof of their wallet address and transactions, they couldn't provide any evidence that they had enough funds.
Here’s what I want to warn all artists in the DeviantArt community or other platforms If you find yourself in a similar situation, be aware that scammers may be targeting you.
My Perspective why I Believe This is a Scam and What the Scammers Gain
From my experience with BTC and crypto since 2017, here's why I believe this situation is a scam, and what the scammers aim to achieve
First, looking at OpenSea, the largest NFT marketplace on the ERC20 network, they do not hold users' funds. Instead, funds from transactions go directly to users’ wallets. OpenSea’s platform fees are also much lower now compared to the crypto bull run in 2020. This alone raises suspicion about the legitimacy of other marketplaces requiring significantly higher fees.
I believe the scammers' tactic is to lure artists into paying these exorbitant minting fees, which go directly into the scammers' wallets. They convince the artists by promising to purchase the art at a higher price, making it seem like there's no risk involved. In reality, the artist has already lost by paying the minting fee, and no purchase is ever made.
In the world of Bitcoin (BTC), the principle is "Trust no one" and “Trustless finality of transactions” In other words, transactions are secure and final without needing trust in a third party.
In the world of Ethereum (ETH), the philosophy is "Code is law" where everything is governed by smart contracts deployed on the blockchain. These contracts are transparent, and even basic code can be read and understood. Promises made by people don’t override what the code says.
I also discuss this issue with art communities. Some people have strongly expressed to me that they want nothing to do with crypto as part of their art process. I completely respect that stance.
However, I believe it's wise to keep your eyes open, have some skin in the game, and not fall into scammers’ traps. Understanding the basics of crypto and NFTs can help protect you from these kinds of schemes.
If you found this article helpful, please share it with your fellow artists.
Until next time Take care
Note
- Both cyber security images are mine , I created and approved by AdobeStock to put on sale
- I'm working very hard to bring all my digital arts into Nostr to build my Sats business here to my another npub "HikariHarmony" npub1exdtszhpw3ep643p9z8pahkw8zw00xa9pesf0u4txyyfqvthwapqwh48sw
Link to my full gallery - Anime girl fanarts : HikariHarmony - HikariHarmony on Nostr - General art : KeshikiRakuen
-
 @ 319ad3e7:cc01d50a
2024-10-08 18:05:44
@ 319ad3e7:cc01d50a
2024-10-08 18:05:44LETTER FROM THE FOUNDER
Welcome to the inaugural edition of the Zap.Cooking newsletter!
What began as a simple idea and a collaborative effort has grown into a vibrant community. Food, in its unique way, transcends culture and connects us all. It’s at the dinner table where we break bread and share our lives. Here, we’ve created a space where people come together to exchange ideas and celebrate a shared passion for cooking and culinary excellence.
This is the Nostr way—a community built on shared ideas and a constructive culture. We are excited to embark on this new journey of sharing a newsletter with friends of Nostr and Zap.Cooking. We hope you enjoy this fresh approach and look forward to many shared recipes and conversations.
Bon appétit!
Seth, Founder of Zap.Cooking
\ __________________
Food Clubs For Life Outside The System
Jack Spirko is the founder and host of The Survival Podcast. In episode 3552, titled "Food Clubs for Life Outside The System," Jack engages in a fascinating two-hour conversation with Joshua Longbrook, who established a food club and hub in Chattanooga, TN, as a means of building a parallel society that respects food freedom and self-sovereignty. Agora Food Club is a private association of members who value natural, organic food and regenerative farming practices, creating and sustaining a locally based alternative food system. In this episode, they discuss the blueprint and what it takes to start a food club in your neighborhood.

Links to YT video and Food Club:
https://www.youtube.com/watch?v=5uPcAfG-9AU

The Six-Ingredient Grandma Betty's Chicken Dijon Family Recipe
https://image.nostr.build/55d3f300fdc4563265f49f729476724f98ff0a062ce7f8d769bf136f0de05cf5.jpg
“Growing up there are a few staple foods that stick with you. For me, it was my Grandma Betty's Chicken Dijon. It was my birthday request every year and every time we cook it up it touches my heart. Grandma Betty passed away 7 years ago. This dish is dedicated to her, directly from her recipe book.” - Quiet Warrior
Grandma Betty's Chicken Dijon on zap.cooking
Glowing Rolls: Raw Vegan Sushi for a Healthy Boost!
https://image.nostr.build/b11da1b878fe48ee74cb1c6c1cc66692ce12827f26c256ecd7a184f99d9c7649.png
“All you need are your favorite vegetables, nori sheets, a bamboo mat, a cutting board, and a knife. For the dip, you can simply use soy sauce, or try this recipe for a delicious creamy dip. I make my own cream cheese with soaked cashews, nutritional yeast, salt, lime juice, and vinegar. You can also find vegan cream cheese or cashew cheese at a health food store. Feel free to add other veggies like bell pepper, chili, cucumber, fresh onion or anything you like! In the image I also used red bell pepper and shiitake.” - Essencial
Glowing Rolls: Raw Vegan Sushi for a Healthy Boost! on zap.cooking
Slow Cookin’ Tender Sweet-and-Sour Brisket
https://image.nostr.build/97a8a78e39fbe4d19f913ea3c7cac9b94ee20d155596a83e241f0fa71a51517a.jpg
“In this case, sweet-and-sour doesn’t mean Americanized Chinese food but rather the sauce that dominated the Shabbos and Pesach dinner table among American Jewish immigrants in the early 20th century.” - Lizsweig
Sweet-and-Sour Brisket on zap.cooking
2024 Nostriga Photo Album
\ Community Photos by AZA_to_₿_myself, Jeroen, elsat, Derek Ross, realjode, and SimplySarah
To share your Nostr community photos, please DM @ZapCooking on Nostr
https://image.nostr.build/388b3bb338672728337ef1c04c90f65655cc29c716f168d35dd4c7343d5802b0.jpg
https://image.nostr.build/011edabbe3f427c60506fddab024bfeb46c72cf5e0a808b562d7c3ace9f239a0.jpg
https://image.nostr.build/5fcb47e3a21bbbedafe245f311b6d43f1f610ad96eec26aa85cdcbd0958fdabf.jpg
https://image.nostr.build/c2eac240326a7e4ab176776c5d140d0017ccdfef89ef733eaf85efda8e0d39f5.jpg
https://image.nostr.build/078682ee987734911886592f377a356245b5a5ea2a15c44ba80e3101ae523b52.jpg
https://image.nostr.build/c28418d851f3ad7f61435813d8aee82d87af3de4472b4d718a1d2573ae7d38c8.jpg
https://image.nostr.build/d3a55e11d7927c7cae106491d00a0cfda8323b976aa29123a0fd4e4e3fe78505.jpg
https://image.nostr.build/bdd055b0b37a9ebcdc91411796ae6cf785338679e7f44aebf1dc721cc09b076c.jpg
https://image.nostr.build/e7bf6c58de70510e96ec3b10630f4a4cfb770026532e2d307b4f95346a4d9ea4.jpg
https://image.nostr.build/b8eb934f8f15aae87ed0db66e898062ec723a8f16d9e93229cd2783d2b158e9d.jpg
https://image.nostr.build/f999d2389c363be56543444f301e443ddc126f1caebb9462b74b800d54ed2c28.jpg
https://image.nostr.build/0ca2d868703298d222f9cabc3e10a73dcd2d1f82f1b22f8526d9360e9bec8cc7.jpg
https://image.nostr.build/94460309bf933bcd89887f16ea6c384fa5bc5e3eb74500de099a3a1405da8edc.jpg
UPCOMING NOSTR HAPPENINGS
To submit your Nostr event, please DM @ZapCooking on Nostr
Nostr Valley @ Happy Valley Brewing Company - October 12, 2024 - 12pm to 4pm (est)
https://image.nostr.build/6c830618389046460ad41e3704864adb338b2a980cc765de51106a2f65adba67.jpg
Nostrville 2.0 No Panels, All Party! @ Bitcoin Park - November 6, 2024 - 4:30pm to 7:30pm (cst)
Nostrville 2.0 - No panels, all party!, Wed, Nov 6, 2024, 4:30 PM | Meetup
ZAP.COOKING PRESENTS: LACE
https://image.nostr.build/fb37dfaa7efe8add086d75af2dfd193181de728e108bd2c8e095a60f7e64bc4f.jpg
\ SimplySarah: Let’s start by learning a little background on Lace. What is your food story?
\ Lace: Food for me runs in my veins. My family is from Jamaica and my grandmother began cooking as a girl. She brought her recipes with her to the UK in the 1950s and cooks the most delicious dishes. My mother has been a professional chef for over 40 years. Family meals at Christmas were always a big deal. However, it wasn't until 18, I began cooking at university where I vowed my children would know how to cook a healthy meal and not end up like the people around me living on take out and micro meals. As a student, I just recreated things I ate at home and when I was unsure, I'd call my mum or my grandmother for help. When I had kids, I put them in the kitchen at age 2 and my eldest, now 15, is an incredible chef. We are also well traveled and always enjoying local cuisine which also inspires our cooking.
SimplySarah: That is a lovely background. It seems it was a natural progression to want to get into writing cookbooks. I understand you are working on your second currently, but let's backtrack and talk about how the first one came to life.
Lace: It would seem so. I always wanted to write a book but a cookbook wasn't what I thought I would write first 😅 And yes, the second is coming next year, a co-authored book. The first, came about because of Facebook, actually. Admittedly, I am one of those people who posts food pictures. And my Facebook followers began asking me for my recipes all the time. And I would write them out... and then decided it made more sense to write them once inside a book and sell it. Hence Lace's Bad Ass Yard Food was born.
https://image.nostr.build/563b2d4299d824ef4fbb8b85749ba1bb24b0fb4025bf6b10fa2ddaed7217240a.jpg
SimplySarah: That's an awesome title! What IS Bad Ass Yard Food?
Lace: Hahaha, thank you! Yard food is what we (as Jamaicans in my family) call our cuisine. Yard food. Yard means home. So it's basically great homemade food. Typically, this is things like Curry Chicken, Fry Fish, Jerk Chicken, Rice and Peas, Hard Food (yam, dumplings and green bananas) and many other things.
SimplySarah: All those dishes sound phenomenal. If you had a go-to dish from the first cookbook what would you select? Maybe something that is always served on a weekly or regular basis at your home?
Lace: Oh they are! My favorite is curry goat. Curry Chicken has got to be the go to, I still cook it weekly now! And no matter where I've lived in the world, I can always prepare it.
https://image.nostr.build/da216e149bee8676a806f010ddde5a29eb4ffa0adeaf5f68265e0e2cc3f11649.jpg
SimplySarah: Funny, I believe you just posted on Nostr that you were in the process of making curry chicken if I recall correctly. Is the next cookbook following the same roots? Or are you and your partner exploring different cuisines?
Lace: That's right! I did just post that curry on Nostr. The next book is going to feature 8 of my favorite recipes. Some will be Jamaican but I also happen to love Asian inspired dishes and have some European favorites too which will be featured. This will be the first time I'm sharing non Caribbean dishes. As for me and my boyfriend, he is Colombian and an ex-military Chef. He has been sharing his food with us and has been enjoying eating food from different regions for the first time as a result of meeting me. It's great fun to bond through food.
Lace’s Curry Chicken with Purple Cabbage, Plantains, and White Rice:\ https://image.nostr.build/fb37dfaa7efe8add086d75af2dfd193181de728e108bd2c8e095a60f7e64bc4f.jpg
SimplySarah: Is he the co-author you are speaking about?
\ Lace: Nope. The other Authors of the book are all entrepreneurs who love food. The first edition will be available in november, it's called Made with Love. I will be featured in the second coming 2025.
SimplySarah: Oh, nice! How did you get tapped into this project?
Lace: Again, my facebook network. I was chatting with a lady who is a self made millionaire about money. She checked out my fb profile and said.. ohh I love your cooking videos, what a fun way to market (my tech business) and then invited me to check out the cookbook project and be part of it. And just like that I was in.
SimplySarah: Facebook definitely brings a lot of people together based on their favorite topics. Now that you are exploring Nostr and have such an incredible background with culinary arts, what do you hope to achieve here on this social protocol?
Lace: Yes, socials are great for that! Honestly, I just want to connect with folks who love great food and are into self development, natural living, love travel and sovereignty. On my second day on Nostr, I met you, a fellow foodie, so it's certainly working out well so far. :) And without all the ads and other crap fb force on it's users
SimplySarah: Personally, I am super thrilled you have joined Nostr. We need more foodies, and I love nerding out about anything food related, especially the food travel stories. I would absolutely love to follow your food journey, and I think all the Nostr foodies should too. Where can everyone find you, follow you, and maybe buy a cookbook?
Lace: Yay! Thank you. I love talking about food, cooking, sharing food, buying ingredients and trying food. You can find me on Facebook - the loved and hated, Nostr, and my personal website. There's no fancy sales page for the cookbook yet! 11 of my Jamaican recipes in one cute ebook :) I'm coming over to Zap Cooking too.
SimplySarah: One day you will be Nostr Only and forget all about Facebook. Haha! We look forward to having you on Zap.Cooking. We have a lot of ideas in the works and would love for you to be involved! I have one final question. First, I want to thank you for taking your time to spend your Saturday morning with me. This was fun. You mentioned you put your children in the kitchen at an early age. I'm a big fan of teaching kids life skills when they are young. Do you have any tips for parents to help them in the kitchen with their children?
Lace: I'm sure that will happen. My fb network has been instrumental in my success and surviving the rough time in my travel. Do tell me all about your ideas for Zap, I'd love to see how I can be involved!
Yes, tips for parents, When kids are eating solids, feed them home cooked meals, no jars, no processed stuff, healthy, varied, adventurous meals you eat. If you're eating octopus, let ‘em try. If you're eating veg, let them try. If you're eating chicken liver pate, let them try. Encourage a varied diet and pallet. Then at 2, get them in the kitchen. Let them peel garlic cloves, add herbs to meat, make meatballs, mix and taste things. Invite them to cook everyday. And have fun with it!
It's been my pleasure to spend time with you this Saturday morning Sarah. Thank YOU.
You can find the talented Lace at:
https://www.facebook.com/iamlaceflowers
https://primal.net/p/npub1ruhmx2wy663u9k2sams6qrlvgq86t3p4q3ygwgp5wqzcrgd6fh7sr20ys2
https://www.iamlaceflowers.com/workwithme
Follow Zap.Cooking Content Coordinator SimplySarah at:
https://image.nostr.build/c208bb8d562421beb00cc26fcf38417a0d52660659f4ac9d40365f3761a486b8.png
-
 @ e6817453:b0ac3c39
2024-10-06 11:21:27
@ e6817453:b0ac3c39
2024-10-06 11:21:27Hey folks, today we're diving into an exciting and emerging topic: personal artificial intelligence (PAI) and its connection to sovereignty, privacy, and ethics. With the rapid advancements in AI, there's a growing interest in the development of personal AI agents that can work on behalf of the user, acting autonomously and providing tailored services. However, as with any new technology, there are several critical factors that shape the future of PAI. Today, we'll explore three key pillars: privacy and ownership, explainability, and bias.
1. Privacy and Ownership: Foundations of Personal AI
At the heart of personal AI, much like self-sovereign identity (SSI), is the concept of ownership. For personal AI to be truly effective and valuable, users must own not only their data but also the computational power that drives these systems. This autonomy is essential for creating systems that respect the user's privacy and operate independently of large corporations.
In this context, privacy is more than just a feature—it's a fundamental right. Users should feel safe discussing sensitive topics with their AI, knowing that their data won’t be repurposed or misused by big tech companies. This level of control and data ownership ensures that users remain the sole beneficiaries of their information and computational resources, making privacy one of the core pillars of PAI.
2. Bias and Fairness: The Ethical Dilemma of LLMs
Most of today’s AI systems, including personal AI, rely heavily on large language models (LLMs). These models are trained on vast datasets that represent snapshots of the internet, but this introduces a critical ethical challenge: bias. The datasets used for training LLMs can be full of biases, misinformation, and viewpoints that may not align with a user’s personal values.
This leads to one of the major issues in AI ethics for personal AI—how do we ensure fairness and minimize bias in these systems? The training data that LLMs use can introduce perspectives that are not only unrepresentative but potentially harmful or unfair. As users of personal AI, we need systems that are free from such biases and can be tailored to our individual needs and ethical frameworks.
Unfortunately, training models that are truly unbiased and fair requires vast computational resources and significant investment. While large tech companies have the financial means to develop and train these models, individual users or smaller organizations typically do not. This limitation means that users often have to rely on pre-trained models, which may not fully align with their personal ethics or preferences. While fine-tuning models with personalized datasets can help, it's not a perfect solution, and bias remains a significant challenge.
3. Explainability: The Need for Transparency
One of the most frustrating aspects of modern AI is the lack of explainability. Many LLMs operate as "black boxes," meaning that while they provide answers or make decisions, it's often unclear how they arrived at those conclusions. For personal AI to be effective and trustworthy, it must be transparent. Users need to understand how the AI processes information, what data it relies on, and the reasoning behind its conclusions.
Explainability becomes even more critical when AI is used for complex decision-making, especially in areas that impact other people. If an AI is making recommendations, judgments, or decisions, it’s crucial for users to be able to trace the reasoning process behind those actions. Without this transparency, users may end up relying on AI systems that provide flawed or biased outcomes, potentially causing harm.
This lack of transparency is a major hurdle for personal AI development. Current LLMs, as mentioned earlier, are often opaque, making it difficult for users to trust their outputs fully. The explainability of AI systems will need to be improved significantly to ensure that personal AI can be trusted for important tasks.
Addressing the Ethical Landscape of Personal AI
As personal AI systems evolve, they will increasingly shape the ethical landscape of AI. We’ve already touched on the three core pillars—privacy and ownership, bias and fairness, and explainability. But there's more to consider, especially when looking at the broader implications of personal AI development.
Most current AI models, particularly those from big tech companies like Facebook, Google, or OpenAI, are closed systems. This means they are aligned with the goals and ethical frameworks of those companies, which may not always serve the best interests of individual users. Open models, such as Meta's LLaMA, offer more flexibility and control, allowing users to customize and refine the AI to better meet their personal needs. However, the challenge remains in training these models without significant financial and technical resources.
There’s also the temptation to use uncensored models that aren’t aligned with the values of large corporations, as they provide more freedom and flexibility. But in reality, models that are entirely unfiltered may introduce harmful or unethical content. It’s often better to work with aligned models that have had some of the more problematic biases removed, even if this limits some aspects of the system’s freedom.
The future of personal AI will undoubtedly involve a deeper exploration of these ethical questions. As AI becomes more integrated into our daily lives, the need for privacy, fairness, and transparency will only grow. And while we may not yet be able to train personal AI models from scratch, we can continue to shape and refine these systems through curated datasets and ongoing development.
Conclusion
In conclusion, personal AI represents an exciting new frontier, but one that must be navigated with care. Privacy, ownership, bias, and explainability are all essential pillars that will define the future of these systems. As we continue to develop personal AI, we must remain vigilant about the ethical challenges they pose, ensuring that they serve the best interests of users while remaining transparent, fair, and aligned with individual values.
If you have any thoughts or questions on this topic, feel free to reach out—I’d love to continue the conversation!
-
 @ 4ba8e86d:89d32de4
2024-10-25 12:45:38
@ 4ba8e86d:89d32de4
2024-10-25 12:45:38A privacidade é uma preocupação crescente para muitos usuários da internet, especialmente quando se trata de pesquisar na web. É aqui que entra o Searx, um buscador de código aberto que se destaca por seu compromisso com a privacidade do usuário.
Searx é um mecanismo de metabusca descentralizado na forma de software livre, sob a licença GNU AGPLv3, desenvolvido pelo programador Húngaro, Adam Tauber, que agrega resultados por volta de 70 serviços de busca. O mecanismo não salva consultas de pesquisa e não repassa ou mesmo vende dados privados a terceiros. Os usuários não são rastreados e além disso, pode ser usado na rede Tor para o anonimato online.
O Searx foi criado em 2011 como um projeto de código aberto, o que significa que seu código-fonte está disponível para todos os usuários e desenvolvedores examinarem e contribuírem para seu desenvolvimento. Como um buscador de código aberto, o Searx não coleta ou armazena dados pessoais de seus usuários, o que o diferencia de grandes buscadores como o Google.
Uma das principais vantagens do Searx é sua capacidade de preservar a privacidade do usuário. Ele não rastreia suas pesquisas e não compartilha dados com terceiros. Ao contrário do Google e outros buscadores que exibem anúncios personalizados com base no histórico de navegação do usuário, o Searx não exibe anúncios.
O Searx é altamente personalizável, o que significa que os usuários podem escolher quais fontes de dados usar para suas pesquisas. O Searx é capaz de buscar resultados em mais de 70 fontes de dados, incluindo Google, Bing, Yahoo, Wikipedia, Reddit, entre outros. Os usuários podem personalizar suas pesquisas para excluir determinadas fontes ou incluir outras, conforme necessário.
Outra vantagem do Searx é a capacidade de utilizar motores de busca especializados. O Searx pode ser configurado para buscar em motores de busca especializados em áreas específicas, como tecnologia, ciência, artes, entre outros. Isso significa que os usuários podem encontrar resultados mais precisos e relevantes para suas pesquisas.
O Searx oferece uma experiência de busca semelhante à do Google, com uma barra de pesquisa simples e fácil de usar. No entanto, ele se destaca pela sua capacidade de preservar a privacidade do usuário e oferecer resultados personalizados e precisos. Como um projeto de código aberto, o Searx está em constante desenvolvimento e melhoria, e os usuários podem contribuir para seu desenvolvimento, sugerindo melhorias e correções.
O Searx é uma excelente opção para aqueles que se preocupam com a privacidade e segurança de seus dados pessoais na internet. Como um buscador de código aberto, ele se destaca por sua transparência e compromisso com a privacidade do usuário, além de oferecer uma experiência de busca personalizada e altamente personalizável. Se você valoriza a privacidade online, experimente o Searx.
https://searx.thegpm.org/
https://github.com/searx/searx
-
 @ 4ba8e86d:89d32de4
2024-10-05 22:04:32
@ 4ba8e86d:89d32de4
2024-10-05 22:04:32Como funciona o PGP.
O texto a seguir foi retirado do capítulo 1 do documento Introdução à criptografia na documentação do PGP 6.5.1. Copyright © 1990-1999 Network Associates, Inc. Todos os direitos reservados.
-O que é criptografia? -Criptografia forte -Como funciona a criptografia? -Criptografia convencional -Cifra de César -Gerenciamento de chaves e criptografia convencional -Criptografia de chave pública -Como funciona o PGP - Chaves • Assinaturas digitais -Funções hash • Certificados digitais -Distribuição de certificados -Formatos de certificado •Validade e confiança -Verificando validade -Estabelecendo confiança -Modelos de confiança • Revogação de certificado -Comunicar que um certificado foi revogado -O que é uma senha? -Divisão de chave
Os princípios básicos da criptografia.
Quando Júlio César enviou mensagens aos seus generais, ele não confiou nos seus mensageiros. Então ele substituiu cada A em suas mensagens por um D, cada B por um E, e assim por diante através do alfabeto. Somente alguém que conhecesse a regra “shift by 3” poderia decifrar suas mensagens. E assim começamos.
Criptografia e descriptografia.
Os dados que podem ser lidos e compreendidos sem quaisquer medidas especiais são chamados de texto simples ou texto não criptografado. O método de disfarçar o texto simples de forma a ocultar sua substância é chamado de criptografia. Criptografar texto simples resulta em um jargão ilegível chamado texto cifrado. Você usa criptografia para garantir que as informações sejam ocultadas de qualquer pessoa a quem não se destinam, mesmo daqueles que podem ver os dados criptografados. O processo de reverter o texto cifrado ao texto simples original é chamado de descriptografia . A Figura 1-1 ilustra esse processo.
https://nostrcheck.me/media/public/nostrcheck.me_5922365650718442651699905288.webp
Figura 1-1. Criptografia e descriptografia
O que é criptografia?
Criptografia é a ciência que usa a matemática para criptografar e descriptografar dados. A criptografia permite armazenar informações confidenciais ou transmiti-las através de redes inseguras (como a Internet) para que não possam ser lidas por ninguém, exceto pelo destinatário pretendido. Embora a criptografia seja a ciência que protege os dados, a criptoanálise é a ciência que analisa e quebra a comunicação segura. A criptoanálise clássica envolve uma combinação interessante de raciocínio analítico, aplicação de ferramentas matemáticas, descoberta de padrões, paciência, determinação e sorte. Os criptoanalistas também são chamados de atacantes. A criptologia abrange tanto a criptografia quanto a criptoanálise.
Criptografia forte.
"Existem dois tipos de criptografia neste mundo: a criptografia que impedirá a sua irmã mais nova de ler os seus arquivos, e a criptografia que impedirá os principais governos de lerem os seus arquivos. Este livro é sobre o último." --Bruce Schneier, Criptografia Aplicada: Protocolos, Algoritmos e Código Fonte em C. PGP também trata deste último tipo de criptografia. A criptografia pode ser forte ou fraca, conforme explicado acima. A força criptográfica é medida no tempo e nos recursos necessários para recuperar o texto simples. O resultado de uma criptografia forte é um texto cifrado que é muito difícil de decifrar sem a posse da ferramenta de decodificação apropriada. Quão díficil? Dado todo o poder computacional e o tempo disponível de hoje – mesmo um bilhão de computadores fazendo um bilhão de verificações por segundo – não é possível decifrar o resultado de uma criptografia forte antes do fim do universo. Alguém poderia pensar, então, que uma criptografia forte resistiria muito bem até mesmo contra um criptoanalista extremamente determinado. Quem pode realmente dizer? Ninguém provou que a criptografia mais forte disponível hoje resistirá ao poder computacional de amanhã. No entanto, a criptografia forte empregada pelo PGP é a melhor disponível atualmente.
Contudo, a vigilância e o conservadorismo irão protegê-lo melhor do que as alegações de impenetrabilidade.
Como funciona a criptografia?
Um algoritmo criptográfico, ou cifra, é uma função matemática usada no processo de criptografia e descriptografia. Um algoritmo criptográfico funciona em combinação com uma chave – uma palavra, número ou frase – para criptografar o texto simples. O mesmo texto simples é criptografado em texto cifrado diferente com chaves diferentes. A segurança dos dados criptografados depende inteiramente de duas coisas: a força do algoritmo criptográfico e o sigilo da chave. Um algoritmo criptográfico, mais todas as chaves possíveis e todos os protocolos que o fazem funcionar constituem um criptossistema. PGP é um criptossistema.
Criptografia convencional.
Na criptografia convencional, também chamada de criptografia de chave secreta ou de chave simétrica , uma chave é usada tanto para criptografia quanto para descriptografia. O Data Encryption Standard (DES) é um exemplo de criptossistema convencional amplamente empregado pelo Governo Federal. A Figura 1-2 é uma ilustração do processo de criptografia convencional.
https://nostrcheck.me/media/public/nostrcheck.me_1563316185075842071699905520.webp
Figura 1-2. Criptografia convencional
Cifra de César.
Um exemplo extremamente simples de criptografia convencional é uma cifra de substituição. Uma cifra de substituição substitui uma informação por outra. Isso é feito com mais frequência compensando as letras do alfabeto. Dois exemplos são o Anel Decodificador Secreto do Capitão Meia-Noite, que você pode ter possuído quando era criança, e a cifra de Júlio César. Em ambos os casos, o algoritmo serve para compensar o alfabeto e a chave é o número de caracteres para compensá-lo. Por exemplo, se codificarmos a palavra "SEGREDO" usando o valor chave de César de 3, deslocaremos o alfabeto para que a terceira letra abaixo (D) comece o alfabeto. Então começando com A B C D E F G H I J K L M N O P Q R S T U V W X Y Z e deslizando tudo para cima em 3, você obtém DEFGHIJKLMNOPQRSTUVWXYZABC onde D=A, E=B, F=C e assim por diante. Usando este esquema, o texto simples, "SECRET" é criptografado como "VHFUHW". Para permitir que outra pessoa leia o texto cifrado, você diz a ela que a chave é 3. Obviamente, esta é uma criptografia extremamente fraca para os padrões atuais, mas, ei, funcionou para César e ilustra como funciona a criptografia convencional.
Gerenciamento de chaves e criptografia convencional.
A criptografia convencional tem benefícios. É muito rápido. É especialmente útil para criptografar dados que não vão a lugar nenhum. No entanto, a criptografia convencional por si só como meio de transmissão segura de dados pode ser bastante cara, simplesmente devido à dificuldade de distribuição segura de chaves. Lembre-se de um personagem do seu filme de espionagem favorito: a pessoa com uma pasta trancada e algemada ao pulso. Afinal, o que há na pasta? Provavelmente não é o código de lançamento de mísseis/fórmula de biotoxina/plano de invasão em si. É a chave que irá descriptografar os dados secretos. Para que um remetente e um destinatário se comuniquem com segurança usando criptografia convencional, eles devem chegar a um acordo sobre uma chave e mantê-la secreta entre si. Se estiverem em locais físicos diferentes, devem confiar em um mensageiro, no Bat Phone ou em algum outro meio de comunicação seguro para evitar a divulgação da chave secreta durante a transmissão. Qualquer pessoa que ouvir ou interceptar a chave em trânsito poderá posteriormente ler, modificar e falsificar todas as informações criptografadas ou autenticadas com essa chave. Do DES ao Anel Decodificador Secreto do Capitão Midnight, o problema persistente com a criptografia convencional é a distribuição de chaves: como você leva a chave ao destinatário sem que alguém a intercepte?
Criptografia de chave pública.
Os problemas de distribuição de chaves são resolvidos pela criptografia de chave pública, cujo conceito foi introduzido por Whitfield Diffie e Martin Hellman em 1975. (Há agora evidências de que o Serviço Secreto Britânico a inventou alguns anos antes de Diffie e Hellman, mas a manteve um segredo militar - e não fez nada com isso.
[JH Ellis: The Possibility of Secure Non-Secret Digital Encryption, CESG Report, January 1970]) A criptografia de chave pública é um esquema assimétrico que usa um par de chaves para criptografia: uma chave pública, que criptografa os dados, e uma chave privada ou secreta correspondente para descriptografia. Você publica sua chave pública para o mundo enquanto mantém sua chave privada em segredo. Qualquer pessoa com uma cópia da sua chave pública pode criptografar informações que somente você pode ler. Até mesmo pessoas que você nunca conheceu. É computacionalmente inviável deduzir a chave privada da chave pública. Qualquer pessoa que possua uma chave pública pode criptografar informações, mas não pode descriptografá-las. Somente a pessoa que possui a chave privada correspondente pode descriptografar as informações.
https://nostrcheck.me/media/public/nostrcheck.me_6137622541655550851699909180.webp
Figura 1-3. Criptografia de chave pública O principal benefício da criptografia de chave pública é que ela permite que pessoas que não possuem nenhum acordo de segurança pré-existente troquem mensagens com segurança. A necessidade de remetente e destinatário compartilharem chaves secretas através de algum canal seguro é eliminada; todas as comunicações envolvem apenas chaves públicas e nenhuma chave privada é transmitida ou compartilhada. Alguns exemplos de criptossistemas de chave pública são Elgamal (nomeado em homenagem a seu inventor, Taher Elgamal), RSA (nomeado em homenagem a seus inventores, Ron Rivest, Adi Shamir e Leonard Adleman), Diffie-Hellman (nomeado, você adivinhou, em homenagem a seus inventores). ) e DSA, o algoritmo de assinatura digital (inventado por David Kravitz). Como a criptografia convencional já foi o único meio disponível para transmitir informações secretas, o custo dos canais seguros e da distribuição de chaves relegou a sua utilização apenas àqueles que podiam pagar, como governos e grandes bancos (ou crianças pequenas com anéis descodificadores secretos). A criptografia de chave pública é a revolução tecnológica que fornece criptografia forte para as massas adultas. Lembra do mensageiro com a pasta trancada e algemada ao pulso? A criptografia de chave pública o tira do mercado (provavelmente para seu alívio).
Como funciona o PGP.
O PGP combina alguns dos melhores recursos da criptografia convencional e de chave pública. PGP é um criptossistema híbrido. Quando um usuário criptografa texto simples com PGP, o PGP primeiro compacta o texto simples. A compactação de dados economiza tempo de transmissão do modem e espaço em disco e, mais importante ainda, fortalece a segurança criptográfica. A maioria das técnicas de criptoanálise explora padrões encontrados no texto simples para quebrar a cifra. A compressão reduz esses padrões no texto simples, aumentando assim enormemente a resistência à criptoanálise. (Arquivos que são muito curtos para compactar ou que não são compactados bem não são compactados.) O PGP então cria uma chave de sessão, que é uma chave secreta única. Esta chave é um número aleatório gerado a partir dos movimentos aleatórios do mouse e das teclas digitadas. Esta chave de sessão funciona com um algoritmo de criptografia convencional rápido e muito seguro para criptografar o texto simples; o resultado é texto cifrado. Depois que os dados são criptografados, a chave da sessão é criptografada na chave pública do destinatário. Essa chave de sessão criptografada com chave pública é transmitida junto com o texto cifrado ao destinatário.
https://nostrcheck.me/media/public/nostrcheck.me_1978130242364857481699910331.webp
Figura 1-4. Como funciona a criptografia PGP A descriptografia funciona ao contrário. A cópia do PGP do destinatário usa sua chave privada para recuperar a chave de sessão temporária, que o PGP usa para descriptografar o texto cifrado criptografado convencionalmente.
https://nostrcheck.me/media/public/nostrcheck.me_1978130242364857481699910331.webp
Figura 1-5. Como funciona a descriptografia PGP A combinação dos dois métodos de criptografia combina a conveniência da criptografia de chave pública com a velocidade da criptografia convencional. A criptografia convencional é cerca de 1.000 vezes mais rápida que a criptografia de chave pública. A criptografia de chave pública, por sua vez, fornece uma solução para
problemas de distribuição de chaves e transmissão de dados. Usados em conjunto, o desempenho e a distribuição de chaves são melhorados sem qualquer sacrifício na segurança.
Chaves.
Uma chave é um valor que funciona com um algoritmo criptográfico para produzir um texto cifrado específico. As chaves são basicamente números muito, muito, muito grandes. O tamanho da chave é medido em bits; o número que representa uma chave de 1024 bits é enorme. Na criptografia de chave pública, quanto maior a chave, mais seguro é o texto cifrado. No entanto, o tamanho da chave pública e o tamanho da chave secreta da criptografia convencional não têm nenhuma relação. Uma chave convencional de 80 bits tem a força equivalente a uma chave pública de 1.024 bits. Uma chave convencional de 128 bits é equivalente a uma chave pública de 3.000 bits. Novamente, quanto maior a chave, mais segura, mas os algoritmos usados para cada tipo de criptografia são muito diferentes e, portanto, a comparação é como a de maçãs com laranjas. Embora as chaves pública e privada estejam matematicamente relacionadas, é muito difícil derivar a chave privada dada apenas a chave pública; no entanto, derivar a chave privada é sempre possível, desde que haja tempo e capacidade computacional suficientes. Isto torna muito importante escolher chaves do tamanho certo; grande o suficiente para ser seguro, mas pequeno o suficiente para ser aplicado rapidamente. Além disso, você precisa considerar quem pode estar tentando ler seus arquivos, quão determinados eles estão, quanto tempo têm e quais podem ser seus recursos. Chaves maiores serão criptograficamente seguras por um longo período de tempo. Se o que você deseja criptografar precisar ficar oculto por muitos anos, você pode usar uma chave muito grande. Claro, quem sabe quanto tempo levará para determinar sua chave usando os computadores mais rápidos e eficientes de amanhã? Houve um tempo em que uma chave simétrica de 56 bits era considerada extremamente segura. As chaves são armazenadas de forma criptografada. O PGP armazena as chaves em dois arquivos no seu disco rígido; um para chaves públicas e outro para chaves privadas. Esses arquivos são chamados de chaveiros. Ao usar o PGP, você normalmente adicionará as chaves públicas dos seus destinatários ao seu chaveiro público. Suas chaves privadas são armazenadas em seu chaveiro privado. Se você perder seu chaveiro privado, não será possível descriptografar nenhuma informação criptografada nas chaves desse anel.
Assinaturas digitais.
Um grande benefício da criptografia de chave pública é que ela fornece um método para empregar assinaturas digitais. As assinaturas digitais permitem ao destinatário da informação verificar a autenticidade da origem da informação e também verificar se a informação está intacta. Assim, as assinaturas digitais de chave pública fornecem autenticação e integridade de dados. A assinatura digital também proporciona o não repúdio, o que significa que evita que o remetente alegue que não enviou realmente as informações. Esses recursos são tão fundamentais para a criptografia quanto a privacidade, se não mais. Uma assinatura digital tem a mesma finalidade de uma assinatura manuscrita. No entanto, uma assinatura manuscrita é fácil de falsificar. Uma assinatura digital é superior a uma assinatura manuscrita porque é quase impossível de ser falsificada, além de atestar o conteúdo da informação, bem como a identidade do signatário.
Algumas pessoas tendem a usar mais assinaturas do que criptografia. Por exemplo, você pode não se importar se alguém souber que você acabou de depositar US$ 1.000 em sua conta, mas quer ter certeza de que foi o caixa do banco com quem você estava lidando. A maneira básica pela qual as assinaturas digitais são criadas é ilustrada na Figura 1-6 . Em vez de criptografar informações usando a chave pública de outra pessoa, você as criptografa com sua chave privada. Se as informações puderem ser descriptografadas com sua chave pública, elas deverão ter se originado em você.
https://nostrcheck.me/media/public/nostrcheck.me_4033165715613998201699910446.webp
Figura 1-6. Assinaturas digitais simples
Funções hash.
O sistema descrito acima apresenta alguns problemas. É lento e produz um enorme volume de dados – pelo menos o dobro do tamanho da informação original. Uma melhoria no esquema acima é a adição de uma função hash unidirecional no processo. Uma função hash unidirecional recebe uma entrada de comprimento variável – neste caso, uma mensagem de qualquer comprimento, até mesmo milhares ou milhões de bits – e produz uma saída de comprimento fixo; digamos, 160 bits. A função hash garante que, se a informação for alterada de alguma forma – mesmo que por apenas um bit – seja produzido um valor de saída totalmente diferente. O PGP usa uma função hash criptograficamente forte no texto simples que o usuário está assinando. Isso gera um item de dados de comprimento fixo conhecido como resumo da mensagem. (Novamente, qualquer alteração nas informações resulta em um resumo totalmente diferente.) Então o PGP usa o resumo e a chave privada para criar a “assinatura”. O PGP transmite a assinatura e o texto simples juntos. Ao receber a mensagem, o destinatário utiliza o PGP para recalcular o resumo, verificando assim a assinatura. O PGP pode criptografar o texto simples ou não; assinar texto simples é útil se alguns dos destinatários não estiverem interessados ou não forem capazes de verificar a assinatura. Desde que uma função hash segura seja usada, não há como retirar a assinatura de alguém de um documento e anexá-la a outro, ou alterar uma mensagem assinada de qualquer forma. A menor alteração em um documento assinado causará falha no processo de verificação da assinatura digital.
https://nostrcheck.me/media/public/nostrcheck.me_2943209062439984111699910538.webp
Figura 1-7. Assinaturas digitais seguras As assinaturas digitais desempenham um papel importante na autenticação e validação de chaves de outros usuários PGP.
Certificados digitais.
Um problema com os criptosistemas de chave pública é que os usuários devem estar constantemente vigilantes para garantir que estão criptografando com a chave da pessoa correta. Num ambiente onde é seguro trocar chaves livremente através de servidores públicos, os ataques man-in-the-middle são uma ameaça potencial. Neste tipo de ataque, alguém publica uma chave falsa com o nome e ID de usuário do destinatário pretendido. Os dados criptografados – e interceptados por – o verdadeiro proprietário desta chave falsa estão agora em mãos erradas. Em um ambiente de chave pública, é vital que você tenha certeza de que a chave pública para a qual você está criptografando os dados é de fato a chave pública do destinatário pretendido e não uma falsificação. Você pode simplesmente criptografar apenas as chaves que foram entregues fisicamente a você. Mas suponha que você precise trocar informações com pessoas que nunca conheceu; como você pode saber se tem a chave correta? Os certificados digitais, ou certs, simplificam a tarefa de estabelecer se uma chave pública realmente pertence ao suposto proprietário. Um certificado é uma forma de credencial. Exemplos podem ser sua carteira de motorista, seu cartão de previdência social ou sua certidão de nascimento. Cada um deles contém algumas informações que identificam você e alguma autorização informando que outra pessoa confirmou sua identidade. Alguns certificados, como o seu passaporte, são uma confirmação importante o suficiente da sua identidade para que você não queira perdê-los, para que ninguém os use para se passar por você.
Um certificado digital são dados que funcionam como um certificado físico. Um certificado digital é uma informação incluída na chave pública de uma pessoa que ajuda outras pessoas a verificar se uma chave é genuína ou válida. Os certificados digitais são usados para impedir tentativas de substituir a chave de uma pessoa por outra.
Um certificado digital consiste em três coisas:
● Uma chave pública.
● Informações do certificado. (Informações de "identidade" sobre o usuário, como nome, ID do usuário e assim por diante.) ● Uma ou mais assinaturas digitais.
O objetivo da assinatura digital em um certificado é afirmar que as informações do certificado foram atestadas por alguma outra pessoa ou entidade. A assinatura digital não atesta a autenticidade do certificado como um todo; ele atesta apenas que as informações de identidade assinadas acompanham ou estão vinculadas à chave pública. Assim, um certificado é basicamente uma chave pública com uma ou duas formas de identificação anexadas, além de um forte selo de aprovação de algum outro indivíduo confiável.
https://nostrcheck.me/media/public/nostrcheck.me_7979578982089845401699910854.webp
Figura 1-8. Anatomia de um certificado PGP
Distribuição de certificados.
Os certificados são utilizados quando é necessário trocar chaves públicas com outra pessoa. Para pequenos grupos de pessoas que desejam se comunicar com segurança, é fácil trocar manualmente disquetes ou e-mails contendo a chave pública de cada proprietário. Esta é a distribuição manual de chave pública e é prática apenas até certo ponto. Além desse ponto, é necessário implementar sistemas que possam fornecer os mecanismos necessários de segurança, armazenamento e troca para que colegas de trabalho, parceiros de negócios ou estranhos possam se comunicar, se necessário. Eles podem vir na forma de repositórios somente de armazenamento, chamados Servidores de Certificados, ou sistemas mais estruturados que fornecem recursos adicionais de gerenciamento de chaves e são chamados de Infraestruturas de Chave Pública (PKIs).
Servidores de certificados.
Um servidor de certificados, também chamado de servidor certificado ou servidor de chaves, é um banco de dados que permite aos usuários enviar e recuperar certificados digitais. Um servidor certificado geralmente fornece alguns recursos administrativos que permitem que uma empresa mantenha suas políticas de segurança – por exemplo, permitindo que apenas as chaves que atendam a determinados requisitos sejam armazenadas.
Infraestruturas de Chave Pública.
Uma PKI contém os recursos de armazenamento de certificados de um servidor de certificados, mas também fornece recursos de gerenciamento de certificados (a capacidade de emitir, revogar, armazenar, recuperar e confiar em certificados). A principal característica de uma PKI é a introdução do que é conhecido como Autoridade Certificadora,ou CA, que é uma entidade humana — uma pessoa, grupo, departamento, empresa ou outra associação — que uma organização autorizou a emitir certificados para seus usuários de computador. (A função de uma CA é análoga à do Passport Office do governo de um país.) Uma CA cria certificados e os assina digitalmente usando a chave privada da CA. Devido ao seu papel na criação de certificados, a CA é o componente central de uma PKI. Usando a chave pública da CA, qualquer pessoa que queira verificar a autenticidade de um certificado verifica a assinatura digital da CA emissora e, portanto, a integridade do conteúdo do certificado (mais importante ainda, a chave pública e a identidade do titular do certificado).
Formatos de certificado.
Um certificado digital é basicamente uma coleção de informações de identificação vinculadas a uma chave pública e assinadas por um terceiro confiável para provar sua autenticidade. Um certificado digital pode ter vários formatos diferentes.
O PGP reconhece dois formatos de certificado diferentes:
● Certificados PGP ● Certificados X.509 Formato do certificado PGP. Um certificado PGP inclui (mas não está limitado a) as seguintes informações: ● O número da versão do PGP — identifica qual versão do PGP foi usada para criar a chave associada ao certificado. A chave pública do titular do certificado — a parte pública do seu par de chaves, juntamente com o algoritmo da chave: RSA, DH (Diffie-Hellman) ou DSA (Algoritmo de Assinatura Digital).
● As informações do detentor do certificado — consistem em informações de “identidade” sobre o usuário, como seu nome, ID de usuário, fotografia e assim por diante. ● A assinatura digital do proprietário do certificado — também chamada de autoassinatura, é a assinatura que utiliza a chave privada correspondente da chave pública associada ao certificado. ● O período de validade do certificado — a data/hora de início e a data/hora de expiração do certificado; indica quando o certificado irá expirar. ● O algoritmo de criptografia simétrica preferido para a chave — indica o algoritmo de criptografia para o qual o proprietário do certificado prefere que as informações sejam criptografadas. Os algoritmos suportados são CAST, IDEA ou Triple-DES. Você pode pensar em um certificado PGP como uma chave pública com um ou mais rótulos vinculados a ele (veja a Figura 1.9 ). Nessas 'etiquetas' você encontrará informações que identificam o proprietário da chave e uma assinatura do proprietário da chave, que afirma que a chave e a identificação andam juntas. (Essa assinatura específica é chamada de autoassinatura; todo certificado PGP contém uma autoassinatura.) Um aspecto único do formato de certificado PGP é que um único certificado pode conter múltiplas assinaturas. Várias ou muitas pessoas podem assinar o par chave/identificação para atestar a sua própria garantia de que a chave pública pertence definitivamente ao proprietário especificado. Se você procurar em um servidor de certificados público, poderá notar que certos certificados, como o do criador do PGP, Phil Zimmermann, contêm muitas assinaturas. Alguns certificados PGP consistem em uma chave pública com vários rótulos, cada um contendo um meio diferente de identificar o proprietário da chave (por exemplo, o nome do proprietário e a conta de e-mail corporativa, o apelido do proprietário e a conta de e-mail residencial, uma fotografia do proprietário — tudo em um certificado). A lista de assinaturas de cada uma dessas identidades pode ser diferente; as assinaturas atestam a autenticidade de que um dos rótulos pertence à chave pública, e não que todos os rótulos da chave sejam autênticos. (Observe que 'autêntico' está nos olhos de quem vê - assinaturas são opiniões, e diferentes pessoas dedicam diferentes níveis de devida diligência na verificação da autenticidade antes de assinar uma chave.)
https://nostrcheck.me/media/public/nostrcheck.me_7979578982089845401699910854.webp
Figura 1-9. Um certificado PGP
Formato de certificado X.509.
X.509 é outro formato de certificado muito comum. Todos os certificados X.509 estão em conformidade com o padrão internacional ITU-T X.509; assim (teoricamente) os certificados X.509 criados para um aplicativo podem ser usados por qualquer aplicativo compatível com X.509. Na prática, porém, diferentes empresas criaram suas próprias extensões para certificados X.509, e nem todas funcionam juntas. Um certificado exige que alguém valide que uma chave pública e o nome do proprietário da chave andam juntos. Com os certificados PGP, qualquer pessoa pode desempenhar o papel de validador. Com certificados X.509, o validador é sempre uma Autoridade Certificadora ou alguém designado por uma CA. (Tenha em mente que os certificados PGP também suportam totalmente uma estrutura hierárquica usando uma CA para validar certificados.)
Um certificado X.509 é uma coleção de um conjunto padrão de campos contendo informações sobre um usuário ou dispositivo e sua chave pública correspondente. O padrão X.509 define quais informações vão para o certificado e descreve como codificá-lo (o formato dos dados). Todos os certificados X.509 possuem os seguintes dados:
O número da versão X.509
— identifica qual versão do padrão X.509 se aplica a este certificado, o que afeta quais informações podem ser especificadas nele. A mais atual é a versão 3.
A chave pública do titular do certificado
— a chave pública do titular do certificado, juntamente com um identificador de algoritmo que especifica a qual sistema criptográfico a chave pertence e quaisquer parâmetros de chave associados.
O número de série do certificado
— a entidade (aplicação ou pessoa) que criou o certificado é responsável por atribuir-lhe um número de série único para distingui-lo de outros certificados que emite. Esta informação é usada de diversas maneiras; por exemplo, quando um certificado é revogado, seu número de série é colocado em uma Lista de Revogação de Certificados ou CRL.
O identificador exclusivo do detentor do certificado
— (ou DN — nome distinto). Este nome pretende ser exclusivo na Internet. Este nome pretende ser exclusivo na Internet. Um DN consiste em múltiplas subseções e pode ser parecido com isto: CN=Bob Allen, OU=Divisão Total de Segurança de Rede, O=Network Associates, Inc., C=EUA (Referem-se ao nome comum, à unidade organizacional, à organização e ao país do sujeito .)
O período de validade do certificado
— a data/hora de início e a data/hora de expiração do certificado; indica quando o certificado irá expirar.
O nome exclusivo do emissor do certificado
— o nome exclusivo da entidade que assinou o certificado. Normalmente é uma CA. A utilização do certificado implica confiar na entidade que assinou este certificado. (Observe que em alguns casos, como certificados de CA raiz ou de nível superior , o emissor assina seu próprio certificado.)
A assinatura digital do emitente
— a assinatura utilizando a chave privada da entidade que emitiu o certificado.
O identificador do algoritmo de assinatura
— identifica o algoritmo usado pela CA para assinar o certificado.
Existem muitas diferenças entre um certificado X.509 e um certificado PGP, mas as mais importantes são as seguintes: você pode criar seu próprio certificado PGP;
● você deve solicitar e receber um certificado X.509 de uma autoridade de certificação
● Os certificados X.509 suportam nativamente apenas um único nome para o proprietário da chave
● Os certificados X.509 suportam apenas uma única assinatura digital para atestar a validade da chave
Para obter um certificado X.509, você deve solicitar a uma CA a emissão de um certificado. Você fornece sua chave pública, prova de que possui a chave privada correspondente e algumas informações específicas sobre você. Em seguida, você assina digitalmente as informações e envia o pacote completo – a solicitação de certificado – para a CA. A CA então realiza algumas diligências para verificar se as informações fornecidas estão corretas e, em caso afirmativo, gera o certificado e o devolve.
Você pode pensar em um certificado X.509 como um certificado de papel padrão (semelhante ao que você recebeu ao concluir uma aula de primeiros socorros básicos) com uma chave pública colada nele. Ele contém seu nome e algumas informações sobre você, além da assinatura da pessoa que o emitiu para você.
https://nostrcheck.me/media/public/nostrcheck.me_4125576093727079591699911294.webp
Figura 1-10. Um certificado X.509 Provavelmente, o uso mais visível dos certificados X.509 atualmente é em navegadores da web.
Validade e confiança Cada usuário em um sistema de chave pública está vulnerável a confundir uma chave falsa (certificado) com uma chave real. Validade é a confiança de que um certificado de chave pública pertence ao seu suposto proprietário. A validade é essencial em um ambiente de chave pública onde você deve estabelecer constantemente se um determinado certificado é autêntico ou não. Depois de ter certeza de que um certificado pertencente a outra pessoa é válido, você pode assinar a cópia em seu chaveiro para atestar que verificou o certificado e que ele é autêntico. Se quiser que outras pessoas saibam que você deu ao certificado seu selo de aprovação, você pode exportar a assinatura para um servidor de certificados para que outras pessoas possam vê-la.
Conforme descrito na seção Infraestruturas de Chave Pública , algumas empresas designam uma ou mais Autoridades de Certificação (CAs) para indicar a validade do certificado. Em uma organização que usa uma PKI com certificados X.509, é função da CA emitir certificados aos usuários — um processo que geralmente envolve responder à solicitação de certificado do usuário. Em uma organização que usa certificados PGP sem PKI, é função da CA verificar a autenticidade de todos os certificados PGP e depois assinar os bons. Basicamente, o objetivo principal de uma CA é vincular uma chave pública às informações de identificação contidas no certificado e, assim, garantir a terceiros que algum cuidado foi tomado para garantir que esta ligação das informações de identificação e da chave seja válida. O CA é o Grand Pooh-bah da validação em uma organização; alguém em quem todos confiam e, em algumas organizações, como aquelas que utilizam uma PKI, nenhum certificado é considerado válido, a menos que tenha sido assinado por uma CA confiável.
Verificando validade.
Uma maneira de estabelecer a validade é passar por algum processo manual. Existem várias maneiras de fazer isso. Você pode exigir que o destinatário pretendido lhe entregue fisicamente uma cópia de sua chave pública. Mas isto é muitas vezes inconveniente e ineficiente. Outra forma é verificar manualmente a impressão digital do certificado. Assim como as impressões digitais de cada ser humano são únicas, a impressão digital de cada certificado PGP é única. A impressão digital é um hash do certificado do usuário e aparece como uma das propriedades do certificado. No PGP, a impressão digital pode aparecer como um número hexadecimal ou uma série das chamadas palavras biométricas, que são foneticamente distintas e são usadas para facilitar um pouco o processo de identificação da impressão digital. Você pode verificar se um certificado é válido ligando para o proprietário da chave (para que você origine a transação) e pedindo ao proprietário que leia a impressão digital de sua chave para você e compare essa impressão digital com aquela que você acredita ser a verdadeira. Isso funciona se você conhece a voz do proprietário, mas como verificar manualmente a identidade de alguém que você não conhece? Algumas pessoas colocam a impressão digital de sua chave em seus cartões de visita exatamente por esse motivo. Outra forma de estabelecer a validade do certificado de alguém é confiar que um terceiro indivíduo passou pelo processo de validação do mesmo. Uma CA, por exemplo, é responsável por garantir que, antes de emitir um certificado, ele ou ela o verifique cuidadosamente para ter certeza de que a parte da chave pública realmente pertence ao suposto proprietário. Qualquer pessoa que confie na CA considerará automaticamente quaisquer certificados assinados pela CA como válidos. Outro aspecto da verificação da validade é garantir que o certificado não foi revogado. Para obter mais informações, consulte a seção Revogação de certificado .
Estabelecendo confiança.
Você valida certificados. Você confia nas pessoas. Mais especificamente, você confia nas pessoas para validar os certificados de outras pessoas. Normalmente, a menos que o proprietário lhe entregue o certificado, você terá que confiar na palavra de outra pessoa de que ele é válido.
Introdutores meta e confiáveis.
Na maioria das situações, as pessoas confiam completamente na CA para estabelecer a validade dos certificados. Isso significa que todos os demais dependem da CA para passar por todo o processo de validação manual. Isso é aceitável até um certo número de usuários ou locais de trabalho e, então, não é possível para a AC manter o mesmo nível de validação de qualidade. Nesse caso, é necessário adicionar outros validadores ao sistema.
Um CA também pode ser um meta- introdutor. Um meta-introdutor confere não apenas validade às chaves, mas também confere a capacidade de confiar nas chaves a outros. Semelhante ao rei que entrega seu selo a seus conselheiros de confiança para que eles possam agir de acordo com sua autoridade, o meta-introdutor permite que outros atuem como introdutores de confiança. Esses introdutores confiáveis podem validar chaves com o mesmo efeito do meta-introdutor. Eles não podem, entretanto, criar novos introdutores confiáveis.
Meta-introdutor e introdutor confiável são termos PGP. Em um ambiente X.509, o meta-introdutor é chamado de Autoridade de Certificação raiz ( CA raiz) e os introdutores confiáveis são Autoridades de Certificação subordinadas . A CA raiz usa a chave privada associada a um tipo de certificado especial denominado certificado CA raiz para assinar certificados. Qualquer certificado assinado pelo certificado CA raiz é visto como válido por qualquer outro certificado assinado pela raiz. Este processo de validação funciona mesmo para certificados assinados por outras CAs no sistema — desde que o certificado da CA raiz tenha assinado o certificado da CA subordinada, qualquer certificado assinado pela CA será considerado válido para outras pessoas dentro da hierarquia. Este processo de verificação de backup por meio do sistema para ver quem assinou cujo certificado é chamado de rastreamento de um caminho de certificação ou cadeia de certificação.
Modelos de confiança.
Em sistemas relativamente fechados, como em uma pequena empresa, é fácil rastrear um caminho de certificação até a CA raiz. No entanto, os usuários muitas vezes precisam se comunicar com pessoas fora do seu ambiente corporativo, incluindo algumas que nunca conheceram, como fornecedores, consumidores, clientes, associados e assim por diante. É difícil estabelecer uma linha de confiança com aqueles em quem sua CA não confia explicitamente. As empresas seguem um ou outro modelo de confiança, que determina como os usuários irão estabelecer a validade do certificado. Existem três modelos diferentes:
Confiança Direta.
Confiança Hierárquica Uma teia de confiança Confiança direta A confiança direta é o modelo de confiança mais simples. Neste modelo, um usuário confia que uma chave é válida porque sabe de onde ela veio. Todos os criptosistemas usam essa forma de confiança de alguma forma. Por exemplo, em navegadores da Web, as chaves raiz da Autoridade de Certificação são diretamente confiáveis porque foram enviadas pelo fabricante. Se houver alguma forma de hierarquia, ela se estenderá a partir desses certificados diretamente confiáveis. No PGP, um usuário que valida as chaves e nunca define outro certificado para ser um introdutor confiável está usando confiança direta.
https://nostrcheck.me/media/public/nostrcheck.me_4681914789296468891699911522.webp
Figura 1-11. Confiança direta
Confiança Hierárquica.
Em um sistema hierárquico, há vários certificados "raiz" a partir dos quais a confiança se estende. Esses certificados podem certificar eles próprios certificados ou podem certificar certificados que certificam ainda outros certificados em alguma cadeia. Considere isso como uma grande “árvore” de confiança. A validade do certificado "folha" é verificada rastreando desde seu certificador até outros certificadores, até que um certificado raiz diretamente confiável seja encontrado.
https://nostrcheck.me/media/public/nostrcheck.me_2764578291212045251699911580.webp
Figura 1-12. Confiança hierárquica
Teia de Confiança.
Uma teia de confiança abrange ambos os outros modelos, mas também acrescenta a noção de que a confiança está nos olhos de quem vê (que é a visão do mundo real) e a ideia de que mais informação é melhor. É, portanto, um modelo de confiança cumulativa. Um certificado pode ser confiável diretamente ou confiável em alguma cadeia que remonta a um certificado raiz diretamente confiável (o meta-introdutor) ou por algum grupo de introdutores.
Talvez você já tenha ouvido falar do termo seis graus de separação, que sugere que qualquer pessoa no mundo pode determinar algum vínculo com qualquer outra pessoa no mundo usando seis ou menos outras pessoas como intermediários. Esta é uma teia de introdutores. É também a visão de confiança do PGP. PGP usa assinaturas digitais como forma de introdução. Quando qualquer usuário assina a chave de outro, ele ou ela se torna o introdutor dessa chave. À medida que esse processo avança, ele estabelece uma rede de confiança.
Em um ambiente PGP, qualquer usuário pode atuar como autoridade certificadora. Qualquer usuário PGP pode validar o certificado de chave pública de outro usuário PGP. No entanto, tal certificado só é válido para outro usuário se a parte confiável reconhecer o validador como um introdutor confiável. (Ou seja, você confia na minha opinião de que as chaves dos outros são válidas apenas se você me considerar um apresentador confiável. Caso contrário, minha opinião sobre a validade das outras chaves é discutível.) Armazenados no chaveiro público de cada usuário estão indicadores de
● se o usuário considera ou não uma chave específica válida
● o nível de confiança que o usuário deposita na chave que o proprietário da chave pode servir como certificador das chaves de terceiros
Você indica, na sua cópia da minha chave, se acha que meu julgamento conta. Na verdade, é um sistema de reputação: certas pessoas têm a reputação de fornecer boas assinaturas e as pessoas confiam nelas para atestar a validade de outras chaves.
Níveis de confiança no PGP.
O nível mais alto de confiança em uma chave, a confiança implícita , é a confiança em seu próprio par de chaves. O PGP assume que se você possui a chave privada, você deve confiar nas ações da sua chave pública relacionada. Quaisquer chaves assinadas pela sua chave implicitamente confiável são válidas.
Existem três níveis de confiança que você pode atribuir à chave pública de outra pessoa:
● Confiança total ● Confiança marginal ● Não confiável (ou não confiável)
Para tornar as coisas confusas, também existem três níveis de validade:
● Válido ● Marginalmente válido ● Inválido
Para definir a chave de outra pessoa como um introdutor confiável, você
- Comece com uma chave válida, que seja.
- assinado por você ou
-
assinado por outro apresentador confiável e então
-
Defina o nível de confiança que você acha que o proprietário da chave tem direito.
Por exemplo, suponha que seu chaveiro contenha a chave de Alice. Você validou a chave de Alice e indica isso assinando-a. Você sabe que Alice é uma verdadeira defensora da validação de chaves de outras pessoas. Portanto, você atribui a chave dela com confiança total. Isso faz de Alice uma Autoridade Certificadora. Se Alice assinar a chave de outra pessoa, ela aparecerá como Válida em seu chaveiro. O PGP requer uma assinatura Totalmente confiável ou duas assinaturas Marginalmente confiáveis para estabelecer uma chave como válida. O método do PGP de considerar dois Marginais iguais a um Completo é semelhante a um comerciante que solicita duas formas de identificação. Você pode considerar Alice bastante confiável e também considerar Bob bastante confiável. Qualquer um deles sozinho corre o risco de assinar acidentalmente uma chave falsificada, portanto, você pode não depositar total confiança em nenhum deles. No entanto, as probabilidades de ambos os indivíduos terem assinado a mesma chave falsa são provavelmente pequenas.
Revogação de certificado.
Os certificados só são úteis enquanto são válidos. Não é seguro simplesmente presumir que um certificado é válido para sempre. Na maioria das organizações e em todas as PKIs, os certificados têm uma vida útil restrita. Isso restringe o período em que um sistema fica vulnerável caso ocorra um comprometimento do certificado.
Os certificados são assim criados com um período de validade programado: uma data/hora de início e uma data/hora de expiração. Espera-se que o certificado seja utilizável durante todo o seu período de validade (seu tempo de vida ). Quando o certificado expirar, ele não será mais válido, pois a autenticidade do seu par chave/identificação não estará mais garantida. (O certificado ainda pode ser usado com segurança para reconfirmar informações que foram criptografadas ou assinadas dentro do período de validade – no entanto, ele não deve ser confiável para tarefas criptográficas futuras.)
Existem também situações em que é necessário invalidar um certificado antes da sua data de expiração, como quando o titular do certificado termina o contrato de trabalho com a empresa ou suspeita que a chave privada correspondente do certificado foi comprometida. Isso é chamado de revogação. Um certificado revogado é muito mais suspeito do que um certificado expirado. Os certificados expirados são inutilizáveis, mas não apresentam a mesma ameaça de comprometimento que um certificado revogado. Qualquer pessoa que tenha assinado um certificado pode revogar a sua assinatura no certificado (desde que utilize a mesma chave privada que criou a assinatura). Uma assinatura revogada indica que o signatário não acredita mais que a chave pública e as informações de identificação pertencem uma à outra, ou que a chave pública do certificado (ou a chave privada correspondente) foi comprometida. Uma assinatura revogada deve ter quase tanto peso quanto um certificado revogado. Com certificados X.509, uma assinatura revogada é praticamente igual a um certificado revogado, visto que a única assinatura no certificado é aquela que o tornou válido em primeiro lugar – a assinatura da CA. Os certificados PGP fornecem o recurso adicional de que você pode revogar todo o seu certificado (não apenas as assinaturas nele) se você achar que o certificado foi comprometido. Somente o proprietário do certificado (o detentor da chave privada correspondente) ou alguém que o proprietário do certificado tenha designado como revogador pode revogar um certificado PGP. (Designar um revogador é uma prática útil, pois muitas vezes é a perda da senha da chave privada correspondente do certificado que leva um usuário PGP a revogar seu certificado - uma tarefa que só é possível se alguém tiver acesso à chave privada. ) Somente o emissor do certificado pode revogar um certificado X.509.
Comunicar que um certificado foi revogado.
Quando um certificado é revogado, é importante conscientizar os usuários potenciais do certificado de que ele não é mais válido. Com certificados PGP, a maneira mais comum de comunicar que um certificado foi revogado é publicá-lo em um servidor de certificados para que outras pessoas que desejem se comunicar com você sejam avisadas para não usar essa chave pública. Em um ambiente PKI, a comunicação de certificados revogados é mais comumente obtida por meio de uma estrutura de dados chamada Lista de Revogação de Certificados, ou CRL, que é publicada pela CA. A CRL contém uma lista validada com carimbo de data e hora de todos os certificados revogados e não expirados no sistema. Os certificados revogados permanecem na lista apenas até expirarem e, em seguida, são removidos da lista — isso evita que a lista fique muito longa. A CA distribui a CRL aos usuários em algum intervalo programado regularmente (e potencialmente fora do ciclo, sempre que um certificado é revogado). Teoricamente, isso impedirá que os usuários usem involuntariamente um certificado comprometido. É possível, no entanto, que haja um período de tempo entre as CRLs em que um certificado recentemente comprometido seja usado.
O que é uma senha?
A maioria das pessoas está familiarizada com a restrição de acesso a sistemas de computador por meio de uma senha, que é uma sequência única de caracteres que um usuário digita como código de identificação.
Uma senha longa é uma versão mais longa de uma senha e, em teoria, mais segura. Normalmente composta por várias palavras, uma frase secreta é mais segura contra ataques de dicionário padrão, em que o invasor tenta todas as palavras do dicionário na tentativa de determinar sua senha. As melhores senhas são relativamente longas e complexas e contêm uma combinação de letras maiúsculas e minúsculas, caracteres numéricos e de pontuação. O PGP usa uma senha para criptografar sua chave privada em sua máquina. Sua chave privada é criptografada em seu disco usando um hash de sua senha como chave secreta. Você usa a senha para descriptografar e usar sua chave privada. Uma senha deve ser difícil de esquecer e difícil de ser adivinhada por outras pessoas. Deve ser algo já firmemente enraizado na sua memória de longo prazo, em vez de algo que você invente do zero. Por que? Porque se você esquecer sua senha, você estará sem sorte. Sua chave privada é total e absolutamente inútil sem sua senha e nada pode ser feito a respeito. Lembra-se da citação anterior neste capítulo?
https://nostrcheck.me/media/public/nostrcheck.me_5284734693832771181699911783.webp
PGP é a criptografia que manterá os principais governos fora dos seus arquivos. Certamente também o manterá fora de seus arquivos. Tenha isso em mente quando decidir alterar sua senha para a piada daquela piada que você nunca consegue lembrar.
Divisão de chave.
Dizem que um segredo não é segredo se for conhecido por mais de uma pessoa. Compartilhar um par de chaves privadas representa um grande problema. Embora não seja uma prática recomendada, às vezes é necessário compartilhar um par de chaves privadas. Chaves de assinatura corporativa, por exemplo, são chaves privadas usadas por uma empresa para assinar – por exemplo – documentos legais, informações pessoais confidenciais ou comunicados de imprensa para autenticar sua origem. Nesse caso, vale a pena que vários membros da empresa tenham acesso à chave privada. No entanto, isto significa que qualquer indivíduo pode agir plenamente em nome da empresa. Nesse caso, é aconselhável dividir a chave entre várias pessoas, de modo que mais de uma ou duas pessoas apresentem um pedaço da chave para reconstituí-la em condições utilizáveis. Se poucas peças da chave estiverem disponíveis, a chave ficará inutilizável. Alguns exemplos são dividir uma chave em três partes e exigir duas delas para reconstituir a chave, ou dividi-la em duas partes e exigir ambas as peças. Se uma conexão de rede segura for usada durante o processo de reconstituição, os acionistas da chave não precisam estar fisicamente presentes para aderirem novamente à chave.
-
 @ 6bae33c8:607272e8
2024-10-25 12:14:12
@ 6bae33c8:607272e8
2024-10-25 12:14:12I had the Rams in my picking pool and Sam Darnold in the Steak League which worked out fine, but the Vikings defense got me just two points for one of my good NFFC teams, so that did not.
-
Sam Darnold can make all the throws, and he moves decently in the pocket. It just seems like he’s missing a “read” gene, and that limits his upside and makes him more likely to be a backup than a long-term answer.
-
Justin Jefferson had like six catches in the first quarter, but finished with only eight. The Rams adjusted well defensively in the second half.
-
Kyren Williams scored again, this time as a receiver. One of the elite fantasy players over the last two years and passes the eye test every time.
-
Puka Nacua dropped his first target, then caught seven out the next eight. He looks all the way back. Cooper Kupp also looked healthy and is unlikely to be traded now that the Rams are back in the thick of it in their divison.
-
I loved seeing Demarcus Robinson catch two TDs because no one used him.
-
Matthew Stafford played a great game, even with the pick. He evaded the rush and threw aggresively down the field against a good defense. With his top receivers back he’ll be startable even in one-QB leagues.
-
-
 @ 4ba8e86d:89d32de4
2024-10-25 12:12:40
@ 4ba8e86d:89d32de4
2024-10-25 12:12:40Projetado para atender tanto a usuários iniciantes quanto avançados, o K-9 Mail apresenta uma ampla gama de recursos e funcionalidades.
Desenvolvido inicialmente por Jesse Vincent em 2008, o K-9 Mail foi concebido como uma opção de código aberto para superar as limitações do aplicativo de e-mail padrão do Android. O nome "K-9" é uma referência ao robô cão da série de televisão "Doctor Who". Desde então, o projeto tem crescido com a colaboração de uma comunidade de desenvolvedores ativos.
O K-9 Mail integra-se aos protocolos de e-mail IMAP e POP3, permitindo aos usuários configurar suas contas de e-mail e sincronizar mensagens diretamente no aplicativo. Além disso, o K-9 Mail oferece suporte a recursos avançados de segurança, como criptografia de e-mail por meio de métodos como S/MIME e OpenPGP, garantindo a proteção das comunicações por e-mail.
O aplicativo K-9 Mail oferece recursos diversos para aprimorar a experiência de e-mail no Android. Entre eles, destacam-se: - Suporte a múltiplas contas de e-mail: Os usuários podem configurar e gerenciar várias contas de e-mail em um único aplicativo. - Criptografia e segurança: O K-9 Mail suporta métodos de criptografia, como S/MIME e OpenPGP, para garantir a segurança das mensagens de e-mail. - Personalização: O aplicativo disponibiliza opções de personalização para ajustar as preferências do usuário, incluindo notificações, sincronização e aparência. - Pesquisa avançada: O K-9 Mail oferece recursos poderosos de pesquisa para facilitar a localização rápida de e-mails específicos. - Gerenciamento de pastas: Os usuários podem organizar suas mensagens em pastas personalizadas, simplificando a localização e organização das mensagens.
O K-9 Mail é uma opção confiável de cliente de e-mail de código aberto para dispositivos Android, oferecendo recursos avançados de gerenciamento, segurança e personalização. Sua comunidade ativa de desenvolvedores continua aprimorando e atualizando o aplicativo, garantindo uma experiência de e-mail eficiente e adaptada às necessidades dos usuários.
https://k9mail.app/
https://github.com/k9mail/k9mail.app
-
 @ 4ba8e86d:89d32de4
2024-10-25 11:40:05
@ 4ba8e86d:89d32de4
2024-10-25 11:40:05A loja Aurora vem com um excelente design, interface de usuário amigável para iniciantes e muitos recursos.
A loja Aurora foi originalmente baseada na loja Yalp de Sergei Yeriomin, mas a versão 3.0 passou do zero para a conclusão seguindo o Material Design reescrito para rodar em todos os dispositivos Android 5.0.
Dentre as diversas características oferecidas pela Aurora Store, destacam-se:
- Login Anônimo: Para garantir sua privacidade, você pode fazer login anonimamente, assegurando que suas atividades permaneçam confidenciais.
- Login do Google: Além do anonimato, a opção de login do Google permite acessar aplicativos pagos e instalar versões beta.
- Falsificação de Dispositivo: Caso um aplicativo não esteja disponível para o seu dispositivo, você pode recorrer à funcionalidade de falsificação de dispositivo, permitindo a instalação.
- Filtragem de Aplicativos F-Droid: A possibilidade de filtrar aplicativos do F-Droid evita que eles apareçam em sua lista de atualizações.
- Aplicativos na Lista Negra: Ao adicionar aplicativos à lista negra, você mantém o Google no escuro quanto aos aplicativos instalados.
A loja de aplicativos se apresenta com um design clássico, apresentando uma capa de apps e jogos em destaque, proporcionando um visual convidativo. A aba de aplicativos instalados permite uma gestão mais eficiente, possibilitando atualizações automáticas para a versão mais recente disponível.
A busca por aplicativos é facilitada por categorias que abrangem diversos interesses, como fotografia, música e áudio, compras, personalização, livros e quadrinhos, entre outras. A eficaz função de busca permite localizar aplicativos específicos de maneira rápida e fácil.
A Aurora Store se diferencia pela tecnologia de pesquisa única, agilizando a descoberta de aplicativos em questão de segundos. Além disso, a loja vem com a licença GPLv3, reforçando seu compromisso com o software livre.
Privacidade é um foco central da Aurora Store, sendo considerada uma excelente alternativa para quem preza por manter suas informações pessoais protegidas. O aplicativo suporta contas pessoais e permite downloads com contas anônimas, assegurando que suas atividades não estejam vinculadas a você.
Com a integração do Exodus, a Aurora Store verifica rastreadores presentes nos códigos dos aplicativos, proporcionando uma visão mais transparente das informações coletadas.
O aplicativo se destaca por ser livre de anúncios e pop-ups, proporcionando uma experiência de uso mais limpa. O suporte ao modo escuro oferece conforto visual em ambientes com pouca luz ou durante a noite.
A Aurora Store é uma alternativa valiosa à Google Play Store, oferecendo um ambiente mais privado, recursos robustos e um design elegante que visa aprimorar a experiência do usuário em busca e gerenciamento de aplicativos.
https://github.com/whyorean/AuroraStore
https://f-droid.org/packages/com.aurora.store/
https://gitlab.com/AuroraOSS/AuroraStore/-/releases
-
 @ bd32f268:22b33966
2024-10-02 17:28:12
@ bd32f268:22b33966
2024-10-02 17:28:12A escolha de algo implica abdicar de uma outra coisa. Quando investimos num determinado item vamos ter custos associados a essa decisão, no entanto a melhor forma de pensar nesses custos não será apenas dinheiro que possamos estar a investir mas em todas as possibilidades de que abdicamos para que possamos investir nesse item.
Suponhamos o seguinte cenário, um milionário decide dar uma esmola a um mendigo no valor de 10€, nesse mesmo dia um pobre passa no mesmo local onde está o mendigo e tendo apenas 10 € na carteira decide dar tudo ao mendigo. Apesar de em termos nominais se tratar da mesma quantia facilmente percebemos que o custo de oportunidade é significativamente diferente para o pobre e para o milionário. Esta aferição do custo de oportunidade superior coloca-nos interessantes questões no que diz respeito às razões particulares que levaram a pessoa a tomar a decisão. É lógico esperar que aquele que incorre no maior custo de oportunidade tem uma forte razão para tomar determinada decisão.
Importante também é esta ideia de que priorizamos umas coisas em detrimento de outras, o pobre pode ter ficado sem almoço ao dar todo o dinheiro que lhe restava, caso fosse assim ele de facto priorizou o donativo ao alimentar-se naquela circunstância.
Quando temos 100€ e temos de escolher entre dois produtos de igual preço (100€ cada um), em condições normais vamos escolher o mais importante para nós, isto é o mais valioso. Estas decisões acontecem partindo do pressuposto que o nosso objetivo é maximizar o valor (aqui entendido subjetivamente). Este tipo de decisões têm ainda um outro fator chave, determinante na priorização das decisões: o tempo.
Sendo um recurso escasso, o tempo cria um incentivo natural para a tomada de decisão dado que não podemos diferir a decisão eternamente. Pensando no exemplo concreto da escolha entre dos produtos referidos sabemos que os produtos não estarão sempre disponíveis, dado que a loja pode fechar e além disso a disponibilidade dos produtos poderá estar condicionada caso o produto seja arrebatado por outra pessoa. Este aspecto implica na nossa decisão na medida em que, quando conscientes disto, temos que tomar uma decisão.
Os estoicos e os religiosos repetem muitas vezes a expressão, memento mori, que significa: “lembra-te que morrerás”. Esta frase pungente serve como um despertador existencial, que nos recorda que este tempo acabará. O facto de lembrarmos da morte acorda-nos para aquilo que devemos priorizar, algo frequente ver-se por exemplo em pessoas que vivem situações traumáticas. Quando ultrapassadas as situações traumáticas, o resultado muitas vezes orienta as pessoas para uma redefinição das prioridades de vida, chamamos a isto o crescimento pós-traumático.
 > “Nos ossos que aqui estamos pelos vossos esperamos” Inscrição numa das portas da Igreja de São Francisco em Évora (Capela dos ossos)
> “Nos ossos que aqui estamos pelos vossos esperamos” Inscrição numa das portas da Igreja de São Francisco em Évora (Capela dos ossos)Além deste aspeto o tempo influi também de numa outra questão, na preferência temporal. Este conceito diz respeito à nossa capacidade ou incapacidade em diferir a nossa gratificação, ou seja, se somos propensos à gratificação imediata dos nossos desejos ou se sacrificamos o presente com o intuito de obter uma recompensa maior no futuro. Este conceito ficou bem ilustrado no famoso teste marshmallow em que um grupo de crianças escolhidas por psicólogos tinham de escolher entre comer um marshmallow no imediato, ou esperar cinco minutos numa sala, tendo o marshmallow à sua frente sem o comer e assim receber o segundo.
No caso das crianças que esperaram podemos concluir uma preferência temporal baixa, ao passo que os que decidiram comer de imediato o marshmallow revelam uma elevada preferência temporal. Para concluir esta ideia de que a preferência temporal influencia na toma de decisão diga-se, as crianças com mais baixa preferência temporal revelam: melhores competências sociais, melhor resposta ao stress, menor probabilidade de obesidade; tendo sido isto concluído em estudos feitos à posteriori neste grupo.
Olhando para estes exemplos podemos ver o quão determinantes estas questões são na forma como tomamos as decisões e estruturamos a nossa hierarquia de valor para que possamos aferir de forma mais exata qual a estratégia que nos permite maximizar este valor. Daqui penso que podemos facilmente perceber que a preferência temporal baixa e o custo de oportunidade elevado são marcadores importantes de que nos podemos estar a mover mais em direção a algo que valorizamos e é importante para nós. Atrevo-me a dizer que se não arriscamos nada, talvez aquilo que temos entre mãos não seja assim tão valioso. A maximização do risco é também a maximização do benefício, contudo isto deve sempre ser temperado pela baixa preferência temporal porque a decisão deve sustentar-se ao teste do tempo, idealmente ser algo que resiste mais à erosão que o tempo impõe àquilo que foi objeto da nossa decisão.
Estes aspetos podem estar presentes quer nas decisões mais triviais como referia, decisões de consumo de bens mas também estão presentes noutras decisões como por exemplo: que tipo de relações procuramos com os outros, se mantemos ou não uma prática religiosa, se somos capazes ou não de negar as nossas vontades e impor a disciplina de procurar a excelência nas virtudes. Tudo isto será influenciado por estes aspetos e sendo conscientes destes mecanismos podemos então traçar um perfil mais ajustado à maximização do valor, não só no presente como no futuro.
-
 @ 4ba8e86d:89d32de4
2024-10-25 11:19:28
@ 4ba8e86d:89d32de4
2024-10-25 11:19:28Uma carteira Samourai em um dispositivo Android com airgap em combinação com o Sentinel é suficiente. Sua seed nunca chega à internet, você cria transações offline com o Sentinel, assinar com sua carteira Samourai offline e as transmite com o Sentinel.
Esse guia foi baseado na postagem da Samourai Wallet , Basicamente vamos seguir o que está escrito abaixo.
https://nostrcheck.me/media/public/nostrcheck.me_9551356128214364941706187762.webp
Vamos Precisa de dois aplicativos pra verificação do aplicativo samourai Wallet.
OpenKeychain HashEasily
Primeiramente baixe a carteira samourai Wallet no Site oficial : https://samouraiwallet.com/download
-Importar a chave pública PGP do desenvolvedor.
-Verifique se a impressão digital hash foi assinada pela chave PGP do desenvolvedor.
-Execute o hash sha256 no arquivo baixado.
-Compare visualmente as duas impressões digitais hash.
-antes de instalação da Samourai wallet desligue rede , Wi-Fi, Bluetooth é coloque em modo avião.
-Instale a Samourai Wallet.
Vídeo com a explicação pra fazer a verificação da carteira Samourai wallet em 1:40 e bem curto vídeo.
https://link.storjshare.io/raw/juf373xj3cmu2ezvjn3lcdm2jygq/production/7beed1e67a931522ad7d5bcba61f764fff154f64eb847f856611d75542b33fbb.MP4
Você Pode baixar e verificar no celular online e passa pro celular offline via cabo OTG ou Bluetooth.
https://nostrcheck.me/media/public/nostrcheck.me_6506239047168614881706190998.webp - Por padrão, a MAINNET está habilitada. Toque em "Ok".
https://nostrcheck.me/media/public/nostrcheck.me_4665959278675525031706191125.webp
-
Começar e avance nas configurações.
-
Vai aparecer esse mensagem pra escolher o local pra guarda o arquivo criptografado com sua passphase e PIN escolha um local ou criar uma pasta nova. No caso não vamos salva , se for utilizar o celular com hardwallet salve o backup.
https://nostrcheck.me/media/public/nostrcheck.me_3282756078392669321706191370.webp
https://nostrcheck.me/media/public/nostrcheck.me_1775948496649077751706191388.webp
Toque em "criar uma nova"
Atenção agora vamos pro próximo passo muito IMPORTANTE e que demanda muita atenção e cuidado. Você vai criar uma passphase pra sua carteira , é padrão tem que ter a passphase.
Atenção! A passphase deve ser algo fácil de lembrar, mas que ao mesmo tempo , não seja tão óbvio.
Use sua imaginação , guarde na sua mente a passphase, não vai no óbvio. Igual a passphase que usei " testesamourai "
https://nostrcheck.me/media/public/nostrcheck.me_3673278837059709561706195580.webp
Toque em “ próximo ”
Agora próximo passo é Definir o Código PIN. PIN pode ter de 5 a 8 números. Novamente escolha um PIN fácil de lembrar mas não tão óbvio.
https://nostrcheck.me/media/public/nostrcheck.me_7682063920335318611706195737.webp
Após escolher o PIN digitar duas vezes vai pra próxima tela só toque em Avança. https://nostrcheck.me/media/public/nostrcheck.me_2169630565955263891706195863.webp
Atenção agora vamos pro próximo passo muito IMPORTANTE e que demanda muita atenção e cuidado. O aplicativo te impede de tira print da tela. Pra você não deixa essa informação importante exporta em nenhum local , não guarde online essa informação.
ESCREVA AS 12 PALAVRAS NO PAPEL.
escreva com calma é atenção de uma forma legível de preferência letra de Forma , Após escreve todas as palavras revise se escreveu corretamente.Você pode escrever em vários papéis pra guarda locais diferentes.
Se voce perde essa palavras , você numca mais terá acesso aos Seus Bitcoin guarde bem as palavras..
https://nostrcheck.me/media/public/nostrcheck.me_6115428046070793411706220149.webp
Apos anotar as palavras no papel só dá toque em “ avança”
Vai aparece a sua passphrase pra você certificar que é exatamente o que você digitou verifique e guarde bem na sua mente de preferencia. https://nostrcheck.me/media/public/nostrcheck.me_9156075966432894981706220507.webp
Ter um toque em “ SKIP” e pronto carteira feita totalmente off-line. https://nostrcheck.me/media/public/nostrcheck.me_5297928365552180711706220777.webp
Depois pra testa se anotou corretamente as Seed pode apagar a carteira e testa backup Seed novamente.
Lado esquerdo superior toque no símbolo do robô depois em "configurações" https://nostrcheck.me/media/public/nostrcheck.me_6061690846490213311706222509.webp
Toque na opção “carteira” https://nostrcheck.me/media/public/nostrcheck.me_9171400908043570781706222485.webp
Na última opção "apagar a carteira de forma segura" https://nostrcheck.me/media/public/nostrcheck.me_1243247222498822271706222578.webp https://nostrcheck.me/media/public/nostrcheck.me_2087393619387830581706222599.webp https://nostrcheck.me/media/public/nostrcheck.me_8707025408907536041706222610.webp
Pronto foi apagado só fazer o procedimento de recuperação da Seed.
Toque na Opção " Restore uma carteira existente"
https://nostrcheck.me/media/public/nostrcheck.me_4898356114912667061706223121.webp
Toque na opção de recuperação da sua carteira de bitcoin com seed e passphase.
https://nostrcheck.me/media/public/nostrcheck.me_6380354635899069741706223161.webp
Após fazer a verificação que deu certo o backup da Seed ,Agora vamos pro próximo passo.
https://nostrcheck.me/media/public/nostrcheck.me_7307761562752931011706223812.webp Prepare-se para configurar sua carteira Sentinel, uma aplicação móvel exclusivamente voltada para visualização que permite monitorar saldos e transações em suas carteiras Bitcoin. Essa carteira é projetada de forma a nunca ter acesso às suas chaves privadas, assegurando a proteção dos seus fundos.
O Sentinel é capaz de rastrear diversos tipos de endereços Bitcoin e chaves públicas estendidas. Além disso, oferece funcionalidades como a criação de PSBTs (transações de bitcoin parcialmente assinadas), permitindo que sejam assinadas offline pela sua carteira Samourai ou carteira de hardware.
Ao utilizar o Sentinel, você pode gerar facilmente endereços de recebimento de bitcoin a partir de qualquer uma das suas chaves públicas rastreadas. Além disso, o aplicativo oferece integração nativa com o Tor, proporcionando roteamento seguro no Sentinel.
Para começar, faça o download da carteira Sentinel no site oficial: https://samouraiwallet.com/download
Realize a mesma verificação feita na primeira etapa com a Samourai Wallet.
Em seguida, toque na opção "Configuração".
https://nostrcheck.me/media/public/nostrcheck.me_8214493108314323431706231322.webp
Toque na opção "configuração"
https://nostrcheck.me/media/public/nostrcheck.me_6272143319509445531706231344.webp
Toque na opção "exibir SegWit ZPUB" Quando você quiser adicionar endereços de sua carteira Samourai ao Sentinel, basta inserir a chave pública estendida (geralmente zpub para endereços SegWit bech32 nativos).
https://nostrcheck.me/media/public/nostrcheck.me_9303936705478476931706231362.webp
Com esse código ou qrcode só basta baixa a carteira de visualização da Samourai a Sentinel e pronto adicionar Zpub pra visualização do saldo. Pronto agora é só apagar a carteira samourai Wallet e desinstalar o app ou ficar com a carteira samourai airgap você cria transações offline com o Sentinel, assinar com sua carteira Samourai offline e as transmite com o Sentinel. Parabéns, você acabou de economizar mais de R$500 em uma "carteira de hardware" para a qual você precisa anotar as 12 palavras de qualquer maneira. Este guia é especialmente dedicado aos iniciantes que estão no início de sua jornada no universo do Bitcoin, buscando opções acessíveis para começar. Ao seguir os passos abaixo, mesmo com recursos limitados, é possível criar uma carteira segura e iniciar sua trajetória no mundo do Bitcoin.
https://medium.com/@alexemidio/samourai-wallet-um-carteira-de-bitcoin-pra-ruas-3003ebb79e57
https://blog.ronindojo.io/discover-version-5-0-0-of-sentinel/
-
-
 @ e6817453:b0ac3c39
2024-09-30 14:52:23
@ e6817453:b0ac3c39
2024-09-30 14:52:23In the modern world of AI, managing vast amounts of data while keeping it relevant and accessible is a significant challenge, mainly when dealing with large language models (LLMs) and vector databases. One approach that has gained prominence in recent years is integrating vector search with metadata, especially in retrieval-augmented generation (RAG) pipelines. Vector search and metadata enable faster and more accurate data retrieval. However, the process of pre- and post-search filtering results plays a crucial role in ensuring data relevance.
The Vector Search and Metadata Challenge
In a typical vector search, you create embeddings from chunks of text, such as a PDF document. These embeddings allow the system to search for similar items and retrieve them based on relevance. The challenge, however, arises when you need to combine vector search results with structured metadata. For example, you may have timestamped text-based content and want to retrieve the most relevant content within a specific date range. This is where metadata becomes critical in refining search results.
Unfortunately, most vector databases treat metadata as a secondary feature, isolating it from the primary vector search process. As a result, handling queries that combine vectors and metadata can become a challenge, particularly when the search needs to account for a dynamic range of filters, such as dates or other structured data.
LibSQL and vector search metadata
LibSQL is a more general-purpose SQLite-based database that adds vector capabilities to regular data. Vectors are presented as blob columns of regular tables. It makes vector embeddings and metadata a first-class citizen that naturally builds deep integration of these data points.
create table if not exists conversation ( id varchar(36) primary key not null, startDate real, endDate real, summary text, vectorSummary F32_BLOB(512) );It solves the challenge of metadata and vector search and eliminates impedance between vector data and regular structured data points in the same storage.
As you can see, you can access vector-like data and start date in the same query.
select c.id ,c.startDate, c.endDate, c.summary, vector_distance_cos(c.vectorSummary, vector(${vector})) distance from conversation where ${startDate ? `and c.startDate >= ${startDate.getTime()}` : ''} ${endDate ? `and c.endDate <= ${endDate.getTime()}` : ''} ${distance ? `and distance <= ${distance}` : ''} order by distance limit ${top};vector_distance_cos calculated as distance allows us to make a primitive vector search that does a full scan and calculates distances on rows. We could optimize it with CTE and limit search and distance calculations to a much smaller subset of data.
This approach could be calculation intensive and fail on large amounts of data.
Libsql offers a way more effective vector search based on FlashDiskANN vector indexed.
vector_top_k('idx_conversation_vectorSummary', ${vector} , ${top}) ivector_top_k is a table function that searches for the top of the newly created vector search index. As you can see, we could use only vector as a function parameter, and other columns could be used outside of the table function. So, to use a vector index together with different columns, we need to apply some strategies.
Now we get a classical problem of integration vector search results with metadata queries.
Post-Filtering: A Common Approach
The most widely adopted method in these pipelines is post-filtering. In this approach, the system first retrieves data based on vector similarities and then applies metadata filters. For example, imagine you’re conducting a vector search to retrieve conversations relevant to a specific question. Still, you also want to ensure these conversations occurred in the past week.
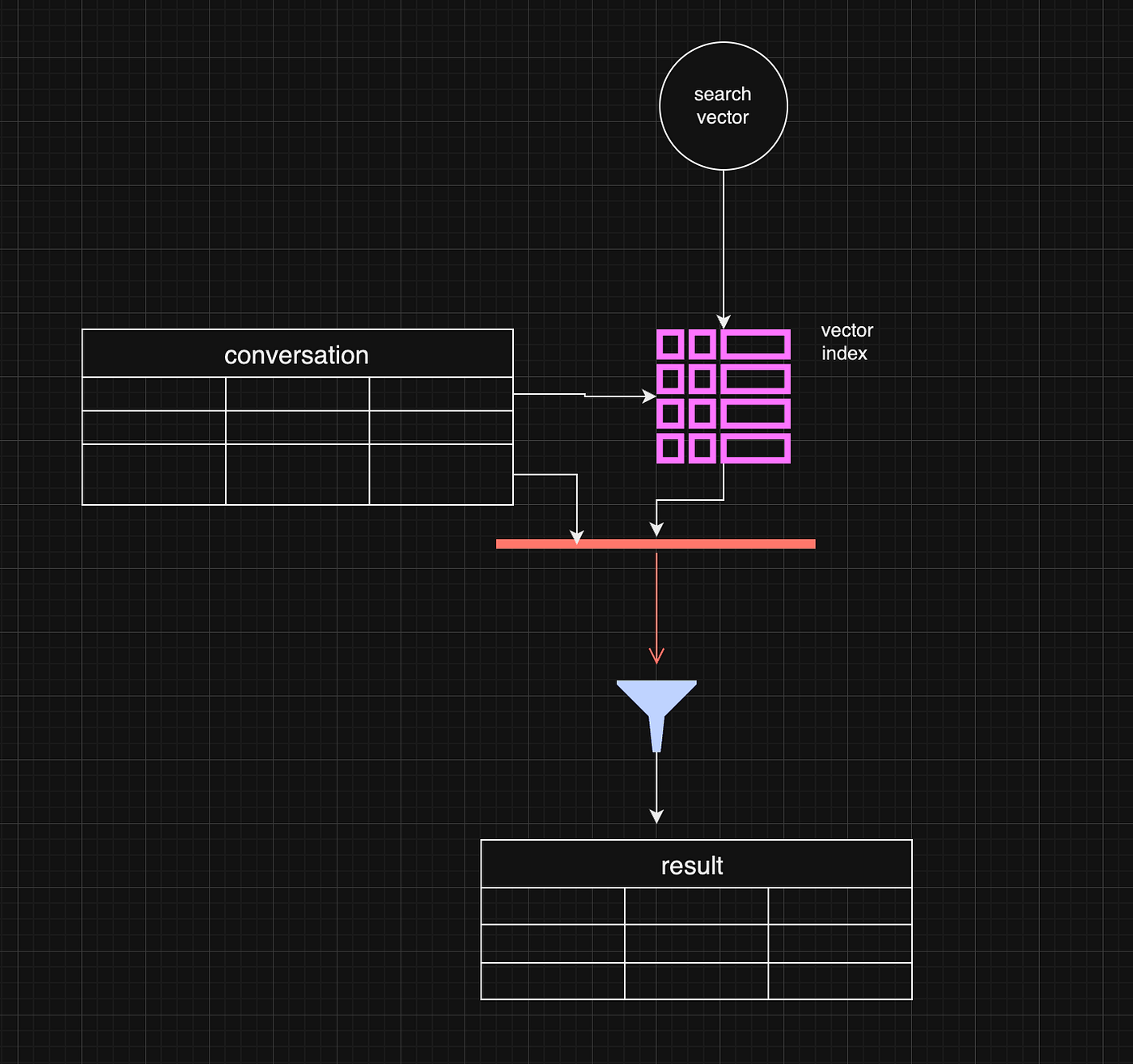
Post-filtering allows the system to retrieve the most relevant vector-based results and subsequently filter out any that don’t meet the metadata criteria, such as date range. This method is efficient when vector similarity is the primary factor driving the search, and metadata is only applied as a secondary filter.
const sqlQuery = ` select c.id ,c.startDate, c.endDate, c.summary, vector_distance_cos(c.vectorSummary, vector(${vector})) distance from vector_top_k('idx_conversation_vectorSummary', ${vector} , ${top}) i inner join conversation c on i.id = c.rowid where ${startDate ? `and c.startDate >= ${startDate.getTime()}` : ''} ${endDate ? `and c.endDate <= ${endDate.getTime()}` : ''} ${distance ? `and distance <= ${distance}` : ''} order by distance limit ${top};However, there are some limitations. For example, the initial vector search may yield fewer results or omit some relevant data before applying the metadata filter. If the search window is narrow enough, this can lead to complete results.
One working strategy is to make the top value in vector_top_K much bigger. Be careful, though, as the function's default max number of results is around 200 rows.
Pre-Filtering: A More Complex Approach
Pre-filtering is a more intricate approach but can be more effective in some instances. In pre-filtering, metadata is used as the primary filter before vector search takes place. This means that only data that meets the metadata criteria is passed into the vector search process, limiting the scope of the search right from the beginning.
While this approach can significantly reduce the amount of irrelevant data in the final results, it comes with its own challenges. For example, pre-filtering requires a deeper understanding of the data structure and may necessitate denormalizing the data or creating separate pre-filtered tables. This can be resource-intensive and, in some cases, impractical for dynamic metadata like date ranges.
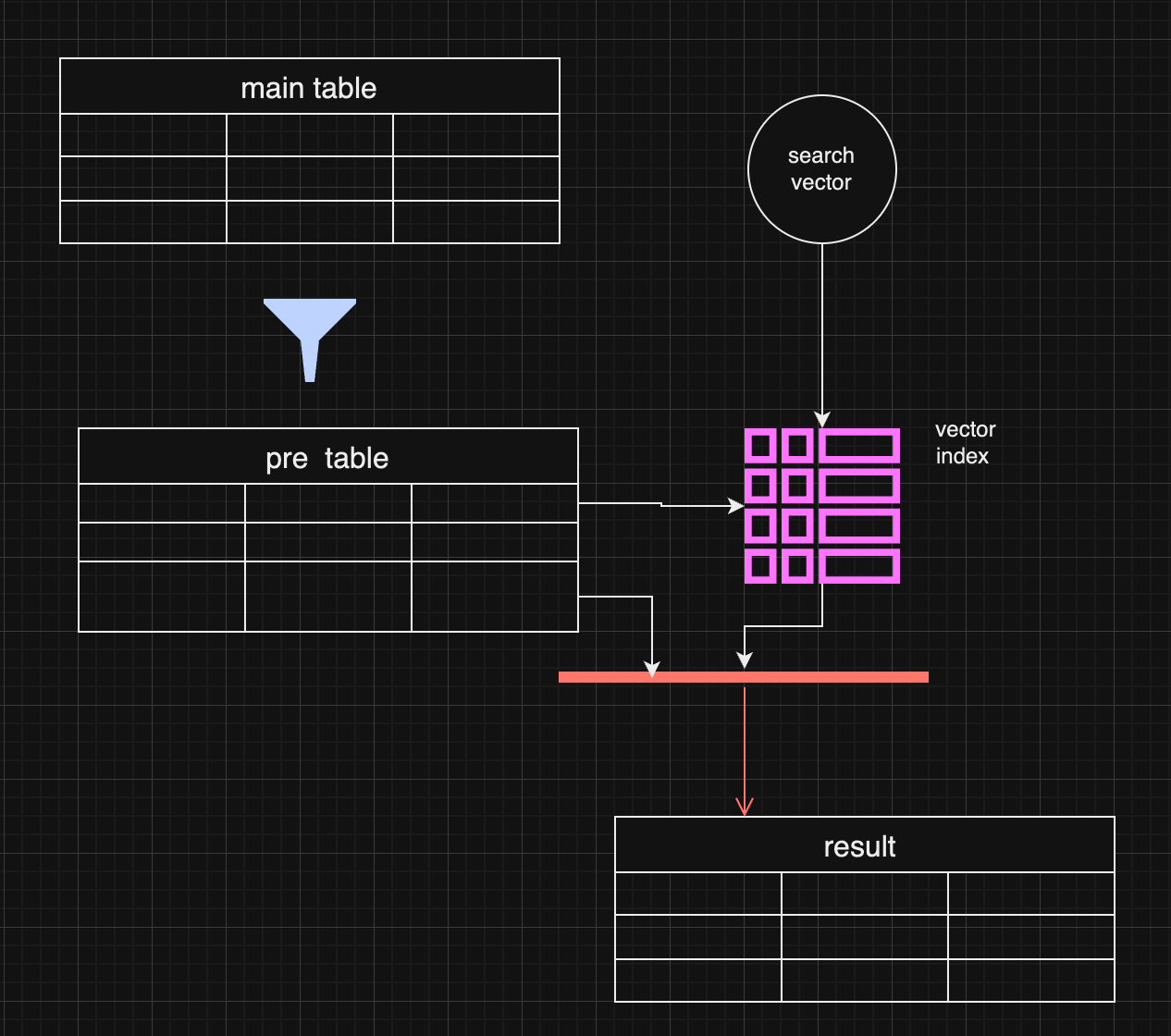
In certain use cases, pre-filtering might outperform post-filtering. For instance, when the metadata (e.g., specific date ranges) is the most important filter, pre-filtering ensures the search is conducted only on the most relevant data.
Pre-filtering with distance-based filtering
So, we are getting back to an old concept. We do prefiltering instead of using a vector index.
WITH FilteredDates AS ( SELECT c.id, c.startDate, c.endDate, c.summary, c.vectorSummary FROM YourTable c WHERE ${startDate ? `AND c.startDate >= ${startDate.getTime()}` : ''} ${endDate ? `AND c.endDate <= ${endDate.getTime()}` : ''} ), DistanceCalculation AS ( SELECT fd.id, fd.startDate, fd.endDate, fd.summary, fd.vectorSummary, vector_distance_cos(fd.vectorSummary, vector(${vector})) AS distance FROM FilteredDates fd ) SELECT dc.id, dc.startDate, dc.endDate, dc.summary, dc.distance FROM DistanceCalculation dc WHERE 1=1 ${distance ? `AND dc.distance <= ${distance}` : ''} ORDER BY dc.distance LIMIT ${top};It makes sense if the filter produces small data and distance calculation happens on the smaller data set.
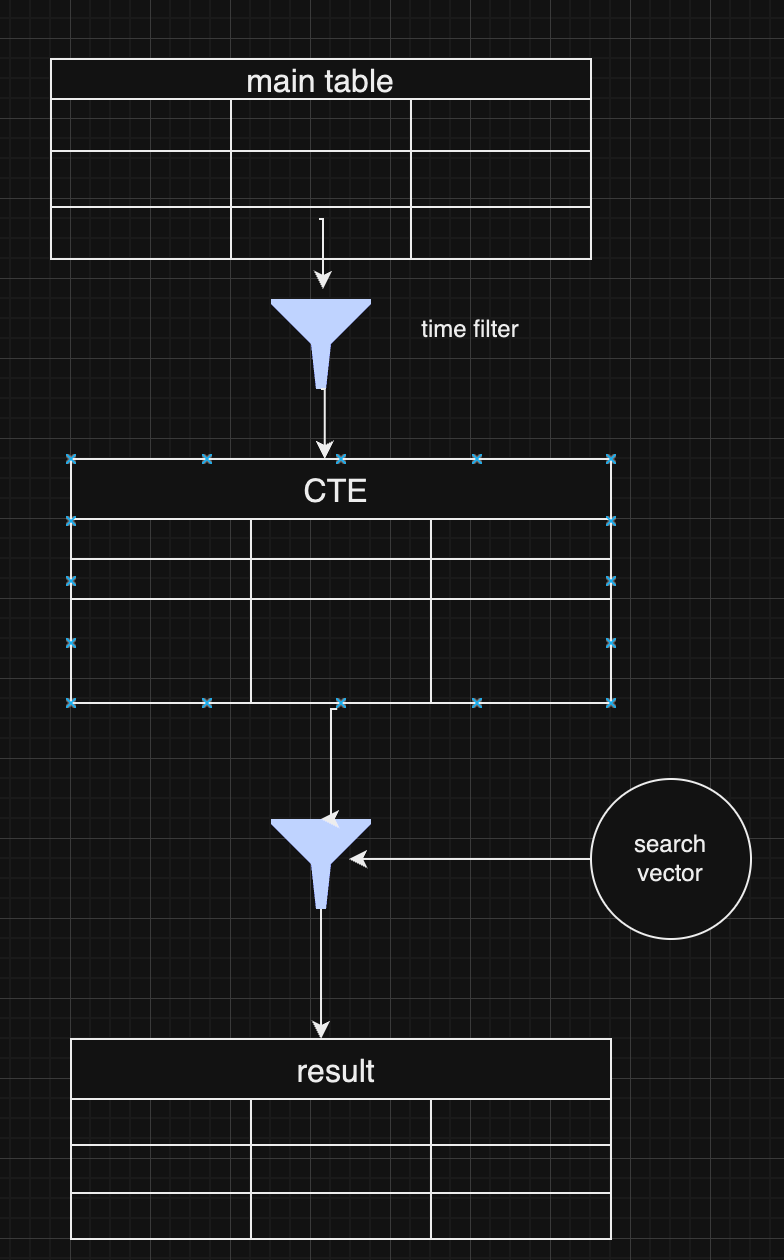
As a pro of this approach, you have full control over the data and get all results without omitting some typical values for extensive index searches.
Choosing Between Pre and Post-Filtering
Both pre-filtering and post-filtering have their advantages and disadvantages. Post-filtering is more accessible to implement, especially when vector similarity is the primary search factor, but it can lead to incomplete results. Pre-filtering, on the other hand, can yield more accurate results but requires more complex data handling and optimization.
In practice, many systems combine both strategies, depending on the query. For example, they might start with a broad pre-filtering based on metadata (like date ranges) and then apply a more targeted vector search with post-filtering to refine the results further.
Conclusion
Vector search with metadata filtering offers a powerful approach for handling large-scale data retrieval in LLMs and RAG pipelines. Whether you choose pre-filtering or post-filtering—or a combination of both—depends on your application's specific requirements. As vector databases continue to evolve, future innovations that combine these two approaches more seamlessly will help improve data relevance and retrieval efficiency further.
-
 @ c4f5e7a7:8856cac7
2024-09-27 08:20:16
@ c4f5e7a7:8856cac7
2024-09-27 08:20:16Best viewed on Habla, YakiHonne or Highlighter.
TL;DR
This article explores the links between public, community-driven data sources (such as OpenStreetMap) and private, cryptographically-owned data found on networks such as Nostr.
The following concepts are explored:
- Attestations: Users signalling to their social graph that they believe something to be true by publishing Attestations. These social proofs act as a decentralised verification system that leverages your web-of-trust.
- Proof of Place: An oracle-based system where physical letters are sent to real-world locations, confirming the corresponding digital ownership via cryptographic proofs. This binds physical locations in meatspace with their digital representations in the Nostrverse.
- Check-ins: Foursquare-style check-ins that can be verified using attestations from place owners, ensuring authenticity. This approach uses web-of-trust to validate check-ins and location ownership over time.
The goal is to leverage cryptographic ownership where necessary while preserving the open, collaborative nature of public data systems.
Open Data in a public commons has a place and should not be thrown out with the Web 2.0 bathwater.
Cognitive Dissonance
Ever since discovering Nostr in August of 2022 I've been grappling with how BTC Map - a project that helps bitcoiners find places to spend sats - should most appropriately use this new protocol.
I am assuming, dear reader, that you are somewhat familiar with Nostr - a relatively new protocol for decentralised identity and communication. If you don’t know your nsec from your npub, please take some time to read these excellent posts: Nostr is Identity for the Internet and The Power of Nostr by @max and @lyn, respectively. Nostr is so much more than a short-form social media replacement.
The social features (check-ins, reviews, etc.) that Nostr unlocks for BTC Map are clear and exciting - all your silos are indeed broken - however, something fundamental has been bothering me for a while and I think it comes down to data ownership.
For those unfamiliar, BTC Map uses OpenStreetMap (OSM) as its main geographic database. OSM is centred on the concept of a commons of objectively verifiable data that is maintained by a global community of volunteer editors; a Wikipedia for maps. There is no data ownership; the data is free (as in freedom) and anyone can edit anything. It is the data equivalent of FOSS (Free and Open Source Software) - FOSD if you will, but more commonly referred to as Open Data.
In contrast, Notes and Other Stuff on Nostr (Places in this cartographic context) are explicitly owned by the controller of the private key. These notes are free to propagate, but they are owned.
How do we reconcile the decentralised nature of Nostr, where data is cryptographically owned by individuals, with the community-managed data commons of OpenStreetMap, where no one owns the data?
Self-sovereign Identity
Before I address this coexistence question, I want to talk a little about identity as it pertains to ownership. If something is to be owned, it has to be owned by someone or something - an identity.
All identities that are not self-sovereign are, by definition, leased to you by a 3rd party. You rent your Facebook identity from Meta in exchange for your data. You rent your web domain from your DNS provider in exchange for your money.
Taken to the extreme, you rent your passport from your Government in exchange for your compliance. You are you at the pleasure of others. Where Bitcoin separates money from the state; Nostr separates identity from the state.
Or, as @nvk said recently: "Don't build your house on someone else's land.".
https://i.nostr.build/xpcCSkDg3uVw0yku.png
While we’ve had the tools for self-sovereign digital identity for decades (think PGP keys or WebAuthN), we haven't had the necessary social use cases nor the corresponding social graph to elevate these identities to the mainstream. Nostr fixes this.
Nostr is PGP for the masses and will take cryptographic identities mainstream.
Full NOSTARD?
Returning to the coexistence question: the data on OpenStreetMap isn’t directly owned by anyone, even though the physical entities the data represents might be privately owned. OSM is a data commons.
We can objectively agree on the location of a tree or a fire hydrant without needing permission to observe and record it. Sure, you could place a tree ‘on Nostr’, but why should you? Just because something can be ‘on Nostr’ doesn’t mean it should be.
https://i.nostr.build/s3So2JVAqoY4E1dI.png
There might be a dystopian future where we can't agree on what a tree is nor where it's located, but I hope we never get there. It's at this point we'll need a Wikifreedia variant of OpenStreetMap.
While integrating Nostr identities into OpenStreetMap would be valuable, the current OSM infrastructure, tools, and community already provide substantial benefits in managing this data commons without needing to go NOSTR-native - there's no need to go Full NOSTARD. H/T to @princeySOV for the original meme.
https://i.nostr.build/ot9jtM5cZtDHNKWc.png
So, how do we appropriately blend cryptographically owned data with the commons?
If a location is owned in meatspace and it's useful to signal that ownership, it should also be owned in cyberspace. Our efforts should therefore focus on entities like businesses, while allowing the commons to manage public data for as long as it can successfully mitigate the tragedy of the commons.
The remainder of this article explores how we can:
- Verify ownership of a physical place in the real world;
- Link that ownership to the corresponding digital place in cyberspace.
As a side note, I don't see private key custodianship - or, even worse, permissioned use of Places signed by another identity's key - as any more viable than the rented identities of Web 2.0.
And as we all know, the Second Law of Infodynamics (no citation!) states that:
"The total amount of sensitive information leaked will always increase over time."
This especially holds true if that data is centralised.
Not your keys, not your notes. Not your keys, not your identity.
Places and Web-of-Trust
@Arkinox has been leading the charge on the Places NIP, introducing Nostr notes (kind 37515) that represent physical locations. The draft is well-crafted, with bonus points for linking back to OSM (and other location repositories) via NIP-73 - External Content IDs (championed by @oscar of @fountain).
However, as Nostr is permissionless, authenticity poses a challenge. Just because someone claims to own a physical location on the Internet doesn’t necessarily mean they have ownership or control of that location in the real world.
Ultimately, this problem can only be solved in a decentralised way by using Web-of-Trust - using your social graph and the perspectives of trusted peers to inform your own perspective. In the context of Places, this requires your network to form a view on which digital identity (public key / npub) is truly the owner of a physical place like your local coffee shop.
This requires users to:
- Verify the owner of a Place in cyberspace is the owner of a place in meatspace.
- Signal this verification to their social graph.
Let's look at the latter idea first with the concept of Attestations ...
Attestations
A way to signal to your social graph that you believe something to be true (or false for that matter) would be by publishing an Attestation note. An Attestation note would signify to your social graph that you think something is either true or false.
Imagine you're a regular at a local coffee shop. You publish an Attestation that says the shop is real and the owner behind the Nostr public key is who they claim to be. Your friends trust you, so they start trusting the shop's digital identity too.
However, attestations applied to Places are just a single use case. The attestation concept could be more widely applied across Nostr in a variety of ways (key rotation, identity linking, etc).
Here is a recent example from @lyn that would carry more signal if it were an Attestation:
https://i.nostr.build/lZAXOEwvRIghgFY4.png
Parallels can be drawn between Attestations and transaction confirmations on the Bitcoin timechain; however, their importance to you would be weighted by clients and/or Data Vending Machines in accordance with:
- Your social graph;
- The type or subject of the content being attested and by whom;
- Your personal preferences.
They could also have a validity duration to be temporally bound, which would be particularly useful in the case of Places.
NIP-25 (Reactions) do allow for users to up/downvote notes with optional content (e.g., emojis) and could work for Attestations, but I think we need something less ambiguous and more definitive.
‘This is true’ resonates more strongly than ‘I like this.’.
https://i.nostr.build/s8NIG2kXzUCLcoax.jpg
There are similar concepts in the Web 3 / Web 5 world such as Verified Credentials by tdb. However, Nostr is the Web 3 now and so wen Attestation NIP?
https://i.nostr.build/Cb047NWyHdJ7h5Ka.jpg
That said, I have seen @utxo has been exploring ‘smart contracts’ on nostr and Attestations may just be a relatively ‘dumb’ subset of the wider concept Nostr-native scripting combined with web-of-trust.
Proof of Place
Attestations handle the signalling of your truth, but what about the initial verification itself?
We already covered how this ultimately has to be derived from your social graph, but what if there was a way to help bootstrap this web-of-trust through the use of oracles? For those unfamiliar with oracles in the digital realm, they are simply trusted purveyors of truth.
Introducing Proof of Place, an out–of-band process where an oracle (such as BTC Map) would mail - yes physically mail- a shared secret to the address of the location being claimed in cyberspace. This shared secret would be locked to the public key (npub) making the claim, which, if unlocked, would prove that the associated private key (nsec) has physical access to the location in meatspace.
One way of doing this would be to mint a 1 sat cashu ecash token locked to the npub of the claimant and mail it to them. If they are able to redeem the token then they have cryptographically proven that they have physical access to the location.
Proof of Place is really nothing more than a weighted Attestation. In a web-of-trust Nostrverse, an oracle is simply a npub (say BTC Map) that you weigh heavily for its opinion on a given topic (say Places).
In the Bitcoin world, Proof of Work anchors digital scarcity in cyberspace to physical scarcity (energy and time) in meatspace and as @Gigi says in PoW is Essential:
"A failure to understand Proof of Work, is a failure to understand Bitcoin."
In the Nostrverse, Proof of Place helps bridge the digital and physical worlds.
@Gigi also observes in Memes vs The World that:
"In Bitcoin, the map is the territory. We can infer everything we care about by looking at the map alone."
https://i.nostr.build/dOnpxfI4u7EL2v4e.png
This isn’t true for Nostr.
In the Nostrverse, the map IS NOT the territory. However, Proof of Place enables us to send cryptographic drones down into the physical territory to help us interpret our digital maps. 🤯
Check-ins
Although not a draft NIP yet, @Arkinox has also been exploring the familiar concept of Foursquare-style Check-ins on Nostr (with kind 13811 notes).
For the uninitiated, Check-ins are simply notes that signal the publisher is at a given location. These locations could be Places (in the Nostr sense) or any other given digital representation of a location for that matter (such as OSM elements) if NIP-73 - External Content IDs are used.
Of course, not everyone will be a Check-in enjoyooor as the concept will not sit well with some people’s threat models and OpSec practices.
Bringing Check-ins to Nostr is possible (as @sebastix capably shows here), but they suffer the same authenticity issues as Places. Just because I say I'm at a given location doesn't mean that I am.
Back in the Web 2.0 days, Foursquare mitigated this by relying on the GPS position of the phone running their app, but this is of course spoofable.
How should we approach Check-in verifiability in the Nostrverse? Well, just like with Places, we can use Attestations and WoT. In the context of Check-ins, an Attestation from the identity (npub) of the Place being checked-in to would be a particularly strong signal. An NFC device could be placed in a coffee shop and attest to check-ins without requiring the owner to manually intervene - I’m sure @blackcoffee and @Ben Arc could hack something together over a weekend!
Check-ins could also be used as a signal for bonafide Place ownership over time.
Summary: Trust Your Bros
So, to recap, we have:
Places: Digital representations of physical locations on Nostr.
Check-ins: Users signalling their presence at a location.
Attestations: Verifiable social proofs used to confirm ownership or the truth of a claim.
You can visualise how these three concepts combine in the diagram below:
https://i.nostr.build/Uv2Jhx5BBfA51y0K.jpg
And, as always, top right trumps bottom left! We have:
Level 0 - Trust Me Bro: Anyone can check-in anywhere. The Place might not exist or might be impersonating the real place in meatspace. The person behind the npub may not have even been there at all.
Level 1 - Definitely Maybe Somewhere: This category covers the middle-ground of ‘Maybe at a Place’ and ‘Definitely Somewhere’. In these examples, you are either self-certifying that you have checked-in at an Attested Place or you are having others attest that you have checked-in at a Place that might not even exist IRL.
Level 2 - Trust Your Bros: An Attested Check-in at an Attested Place. Your individual level of trust would be a function of the number of Attestations and how you weigh them within your own social graph.
https://i.nostr.build/HtLAiJH1uQSTmdxf.jpg
Perhaps the gold standard (or should that be the Bitcoin standard?) would be a Check-in attested by the owner of the Place, which in itself was attested by BTC Map?
Or perhaps not. Ultimately, it’s the users responsibility to determine what they trust by forming their own perspective within the Nostrverse powered by web-of-trust algorithms they control. ‘Trust Me Bro’ or ‘Trust Your Bros’ - you decide.
As we navigate the frontier of cryptographic ownership and decentralised data, it’s up to us to find the balance between preserving the Open Data commons and embracing self-sovereign digital identities.
Thanks
With thanks to Arkinox, Avi, Ben Gunn, Kieran, Blackcoffee, Sebastix, Tomek, Calle, Short Fiat, Ben Weeks and Bitcoms for helping shape my thoughts and refine content, whether you know it or not!
-
 @ e83b66a8:b0526c2b
2024-09-26 19:29:43
@ e83b66a8:b0526c2b
2024-09-26 19:29:43If you’re thinking of buying a Bitaxe, here is some information about pools vs solo mining.
Firstly, although the terms are clear “pool mining”, “solo mining” there is nuance in these definitions, so I want to explain these terms fully.
Solo mining pools exist, such as: https://solo.ckpool.org/
It is called a pool, because you are using their credentials to mine, but you keep all the rewards if you win a block. Despite the name, this is not a pool.
You then have a pool such as https://ocean.xyz/ who are a pool, you use their credentials to mine, and you earn a share of their income relative to your contribution in hash power.
There has been some publicity about a solo miner winning a pool recently, there were about 12 blocks won in 2023 by solo miners. However a winning solo miner is likely to be a server farm with hundreds or even thousands of S19’s or S21’s sharing the same payout wallet address. The image of a home miner with a Bitaxe winning a block is extremely unlikely.
A solo miner is defined as a group of miners that share a payout wallet address, so for example you could have 10 Bitaxe’s at home all configured with the same BTC wallet address, this is considered a single solo miner. And so it is with mid tier mining farms, often privately owned, who have a number of machines set to the same payout address. Most of the time, they share earnings for a more reliable income, but the owner may decide to gamble on winning a block and so choose to solo (lottery) mine.
So far, my Bitaxe, which has been running for 4 days now and is part of the Ocean pool. It is earning about 50 Sats a day. If I were to wait for an on-chain payout, it would take around 60 years to receive one. I can, however, setup a BOLT12 lightning payout address and earn this tiny income through Lightning.
So here’s my recommendation.
Currently, there are two pools that control more than 50% of mining, Foundry USA and AntPool. This is a dangerous position and in fact Bitmain, who provide around 90% of all mining hardware actually invest and have stakes in these and several other pools. This is centralising mining and could potentially allow a 51% attack, which could compromise Bitcoin.
Jack Dorsey is currently developing competing mining hardware chipset, through his company Block and Ocean are attempting to decentralise the pools by building a truly independent option for miners to join.
If you buy a Bitaxe, the best way you can help alleviate the dominance of Bitmain is to join a true pool like Ocean to slowly move control away from the dominant pools.
Bear in mind that many of the other smaller pools are still controlled by Bitmain.
If you're still interested in lottery mining, here are your chances of winning a block:
Represented as Hash rates of different miners:
Nerdminer: 20 KH/s = 20,000 H/s
Bitaxe: 750 GH/s = 750,000,000,000 H/s
Bitmain Antminer S9: 13.5 TH/s = 13,500,000,000,000 H/s
Bitmain Antminer S19: 110TH/s = 110,000,000,000,000 H/s
Bitmain Antminer S21: 200TH/s = 200,000,000,000,000 H/s
Current Global Hash rate 628EH/s (Sept 2024) = 628,000,000,000,000,000,000
If you're running a Bitaxe, your percentage chance of winning a block is: 0.000000119426751592357%
Over a year, your chances increase to: 0.00627707006369428%
Your chances of winning the UK national lottery (assuming 20M tickets sold and you buy one):
0.000005%
Over a year, your chances increase to: 0.00026%
Like in all things in Bitcoin, I don’t ask you to trust me. If you want to verify, here are the references I used in making my conclusions:
https://protos.com/chart-when-solo-miners-found-a-bitcoin-block/
https://investors.block.xyz/investor-news/news-details/2024/Blocks-New-Bitcoin-Mining-Chip-to-Be-Part-of-an-Ongoing-Project-With-Core-Scientific-to-Decentralize-Mining-Hardware/default.aspx
https://www.youtube.com/watch?v=Wo91DWvZRs8
https://i.nostr.build/9rQ9Plv6XQYtt6xd.jpg
-
 @ a9434ee1:d5c885be
2024-09-26 10:42:52
@ a9434ee1:d5c885be
2024-09-26 10:42:521. Relay = Community?
If spinning up a relay is getting easier and cheaper by the day, why can't the relays literally be the group/community?
Then: * Any relay is by default a public community. The more restricted read- or write-access is, the more it becomes a private group. * Any publication targeted at (h-tag) and stored, and thus accepted, by a relay can be seen as a publication in that community. * All-in-1 hosting solutions (integrated blossom servers, lightning nodes, ...) are made easier.
2. Why invent new kinds?
Why can't Kind 1 posts that are targeted and accepted by a relay (i.e. community) just be the forum-posts of that community? Why create new kinds for this? And even weirder, why create a new kind with that exclusively serves as a reply to that new kind? Why not just use generic replies (kind 1111) and take the #otherstuff (event kinds and apps) as an opportunity to introduce those?
For chat messages, however, I get it. You need a kind + reply-kind for those.
3. Community VS Private group
It seems like the only distinction you really need, both for the user and the apps implementing all this, is:
1. Public Community: anyone can read and follow this community but for writing the admins can set limits (pricing, white listings, ...) 2. Private group: only the profiles that even know this relay (i.e. group) exists can interact with it. Read-access has to be granted (invite, pricing, ...) and admins can set limits for writing too. Beyond this distinction it's a bit naive to try to categorize them. Open vs Closed doesn't really mean much for example, since technically all groups/communities set limits and are thus closed. It's more interesting to look the ways in which they can be closed and build on the simplest distinctions you can make there.The difference between Public communities and private groups is the most important one because they both have very different UX and specification requirements:
Memberlist
Communities: None existent
Anyone can read and follow. It just has limits on who can publish what, when. So the most interesting thing to surface is probable something like a list of most active members or a highlighted set of profiles that have special characteristics within this community (top supporter, god-mode, resident artist, ...).
Private Groups: Necessary for it's existence
The whitelisted npubs for read-access are the members.Moderation actions
Both types of groups need a way for the admin(s) to:
* Block/remove users * Remove events * Edit metadata (name, description, guidelines...) * Specify who can write publish what, under what conditionOnly private groups need a way for the admin(s) to:
* Add/approve new members → specify who has read-access, under what conditionGeneralizing too many actions like
add member,join request, etc... that are only applicable to one of these categories just creates bad UX for the other one. You don't "add a member" to a public community. People can follow it without asking anyone's permission (ok yes, some will AUTH for reading but that's besides the point). Some of its followers will then just choose to publish something there and the admin either allows them or not.Having a common protocol for specifying the conditions for this write-access interoperably (as mentioned above) is what I would like to see instead: * Both Communities and Private groups need it anyway * You have to assume admins need granularity in the conditions they set for publishing in their group/community: Who, what, under what condition, ... * You don't want to link out to custom websites (or similar) explaining their allowance schemes
Sidenote: we need a similar kind of spec for the services that allow you to spin up your hosting solution (relay, server, node, ...) so that, when you click "Create new community" in an app, those services can be surfaced. With their business models (including options to self-host parts of it) just there, in the app, without linking out. Same for the lines of communication and payments that are needed to make those business models work from within any app.
Publication and Discovery
Only Communities allow for the exciting possibility of publishing something in multiple overlapping communities at once. Someone writing about how Bees are Capitalists can target their article at the communities that most overlap with its content (and with the author's means and write-access of course). Members of a community around beekeeping can organically discover content and communities on Austrian economics relevant to them.
With Private groups publication happens only in the group and discovery is blocked on purpose.
-
 @ 862fda7e:02a8268b
2024-09-24 01:14:40
@ 862fda7e:02a8268b
2024-09-24 01:14:40The media, government, and "elite" (who are only elite in this low vibration illusion we call "life") are afraid of people like me because I do not accept the reality they have forced us into. My manifesto is an attempt to wake you up from ideas you have been conditioned into believing because it benefits one class - the protected class known as the "elite".
The elite would like to have you believe that my message is something crafted from hatred and they would like to label me with mental issues. They would like you to think I am some crazy extremist who wants to advocate for the harm of others. They would like you to think that I am enciting violence.
This could not be further from the truth.
I am not and will never be an extremist, white supermicist, terrorist, radical, hateful human being. I do not believe in killing in order to convey a message or movement. I do not believe in division.
I only advocate that you become conscious of the reality around us. The reality is that this is a world controlled by the most evil, controlling, destructive freaks. These people work to make sure we are essentially slaves to a system that benefits those who created the system - the elites. Let me make this clear: I do NOT advocate for violence, destruction, death, killing, murder, hatred, division, or terrorism. The elite are threatened by people like me, because they know that we know their game. We know their plans are to destroy, to advocate for violence, to kill, murder, to encite hatred and division. This is all the elite do - they cannot fathom having people live in peace because it isn't beneficial if you want to control the world.
So while you may think it's impossible there is a group of a few evil people who control the world - look back at history. It has always been littered with the few evil who control the many. It would be stupid to think it would be different
-
 @ 08f96856:ffe59a09
2024-09-22 13:02:22
@ 08f96856:ffe59a09
2024-09-22 13:02:22สวัสดีครับเพื่อน ๆ ชาว #siamstr วันนี้ผมจะมาแนะนำ Meshtastic เครื่องมือสื่อสารที่ไร้ศูนย์กลางที่เพื่อน ๆ ไม่ควรพลาดเป็นอันขาด!! เพราะมันคือเครือข่ายการสื่อสารที่ใช้เทคโนโลยี LoRa (Long Range Radio) ซึ่งสามารถส่งข้อความได้ไกลมาก ๆ เป็นกิโลเลยทีเดียว ที่สำคัญไม่ต้องพึ่งพาโครงสร้างพื้นฐานของอินเทอร์เน็ตและไร้การสอดส่องและควบคุมจากรัฐ
Meshtastic คืออะไร?
Meshtastic จะสร้างเครือข่าย "mesh" โดยที่ทุกอุปกรณ์ในเครือข่ายจะช่วยกันรับส่งข้อความต่อ ๆ กันไป ทำให้ทุกคนในเครือข่ายสามารถรับข้อความได้ แม้ว่าจะอยู่ไกลแค่ไหน นอกจากนี้ ข้อความทั้งหมดจะถูก เข้ารหัสไว้ ทำให้เฉพาะผู้ส่งและผู้รับเท่านั้นที่สามารถอ่านได้ ส่วนอุปกรณ์ที่ส่งต่อข้อความจะไม่สามารถเข้าถึงเนื้อหาได้เลย ในการใช้งานนั้นเพื่อน ๆ สามารถเชื่อมต่ออุปกรณ์ Meshtastic เข้ากับโทรศัพท์มือถือเพื่อทุกคนในเครืองข่ายสามารถสื่อสารกันได้ง่าย ๆ ผ่านแอปส่งข้อความบนมือถือ
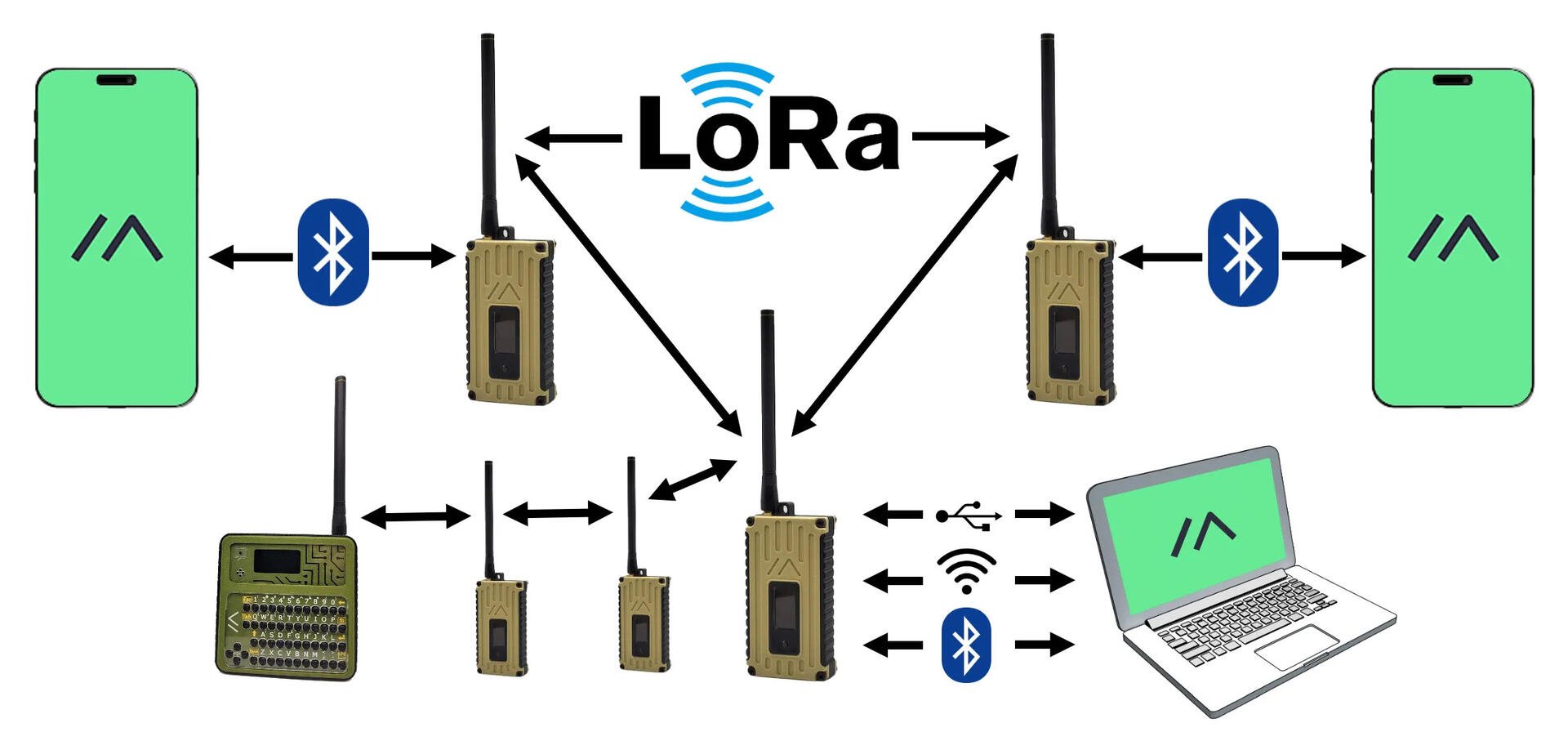
จับมือทำ เริ่มต้นใช้งาน Meshtastic แบบง่าย ๆ
เพื่อน ๆ อยากลองใช้ Meshtastic แล้วใช่มั้ย? มาดูขั้นตอนง่ายๆ กันเลยครับ
1. หาซื้ออุปกรณ์ที่ต้องใช้
ขั้นแรกเลย เราต้องมีอุปกรณ์ LoRa กันก่อนครับ ส่วนตัวผมแนะนำบอร์ด LoRa32 ของ LILYGO ครับ เพราะหาซื้อในไทยและต่างประเทศได้ง่ายมาก โดยจะมีให้เลือกหลายรุ่นมากตามความชอบและการใช้งาน ผมได้ทำตารางเปรียบเทียบคุณสมบัติของแต่ละรุ่นดังนี้ | Name | MCU | RF option | Battery | GPS | Link | | --- | --- | --- | --- | --- | --- | | Lora32 2.1-1.6 | ESP32 | 433/868/915/923 Mhz | no | no | https://a.aliexpress.com/_opRiKMR | | Lora32 T3S3 | ESP32 | 433/868/915 Mhz / 2.4 GHz | no | no | https://a.aliexpress.com/_opRiKMR | | T-Beam v1.1 | ESP32 | 433/868/915/923 Mhz | has batt slot | yes | https://a.aliexpress.com/_oneeH43 | | T-Watch S3 | ESP32 | 433/868/915 Mhz | yes | no | https://a.aliexpress.com/_olkXkLlData | | T-Deck | ESP32 | 433/868/915 Mhz | yes | no | https://a.aliexpress.com/_olkXkLlData | | T-Echo | nRF52840 | 433/868/915 Mhz | yes | yes | https://a.aliexpress.com/_olkXkLlData |

คุณสมบัติสำคัญที่ควรพิจารณาเป็นหลักในการเลือกอุปกรณ์เลยคือความถี่คลื่นวิทยุ (radio frequency) ครับ เพราะการเลือกความถี่สำหรับใช้งานกับ Meshtastic นั้นขึ้นอยู่กับหลายปัจจัย เช่น กฎระเบียบในประเทศ, ระยะทางที่ต้องการสื่อสาร, และความหนาแน่นของสัญญาณในพื้นที่นั้นๆ อุปกรณ์ LoRa ทำงานที่ความถี่ต่างกันในแต่ละภูมิภาค ตามกฎระเบียบในแต่ละประเทศ เช่น สหรัฐอเมริกาใช้คลื่น 915 MHz, ยุโรปใช้ 868 MHz สำหรับประเทศไทยความถี่ที่ได้รับอนุญาตและไม่มีข้อจำกัดในการใช้งานมีดังนี้ครับ: * 433 MHz: ความถี่นี้เป็นที่นิยมใช้ในหลายประเทศรวมถึงในยุโรปสำหรับอุปกรณ์ที่ใช้พลังงานต่ำและไม่ต้องขอใบอนุญาต (LPWAN) เหมาะสำหรับการใช้งานส่งสัญญานได้ไกลเพราะความยาวคลื่นยาวที่สุดในบรรดาตัวเลือกทั้งหมด * 923 MHz: ความถี่นี้ใช้ได้ในหลายประเทศในเอเชีย รวมถึงประเทศไทยที่อนุญาตให้ใช้อุปกรณ์ IoT ที่สื่อสารระยะไกลอย่าง LoRa ได้รับอนุญาตให้สามารถส่งสัญญาณได้ด้วยกำลังงาน (50mW) ที่สูงกว่าคลื่น 433 MHz (10mW) ถือว่าเป็นความถี่ที่เหมาะสำหรับการใช้งานในไทย * 2.4 GHz: เป็นความถี่ที่ใช้กันทั่วโลก และนิยมใช้กับอุปกรณ์หลายประเภท เช่น Wi-Fi และ Bluetooth ความถี่นี้สามารถใช้ในทั่วโลกได้อย่างเสรี แต่มีระยะการส่งสัญญาณที่สั้นกว่าและไม่ค่อยทะลุทะลวงสิ่งกีดขวางได้ดีนัก เหมาะกับพื้นที่ในเมือง
ส่วนตัวผมเลือกใช้ความถี่ 433 MHz เพราะมันทะลุทะลวงสิ่งกีดขวางได้ดี เหมาะกับการใช้งานในพื้นที่ที่มีสิ่งกีดขวางเยอะ เช่น ป่าเขา และช่วยให้การสื่อสารครอบคลุมระยะทางไกลโดยไม่ต้องพึ่งอินเทอร์เน็ตครับ
2. ประกอบอุปกรณ์
เมื่ออุปกรณ์มาถึง ก็จัดการประกอบเลย! อย่าลืมต่อเสาอากาศและแบตเตอรี่ (ถ้ามี) ให้เรียบร้อยก่อนเปิดเครื่องล่ะ ถ้ารุ่นที่ไม่มีแบตก็ต้องหา power bank อแดปเตอร์จ่ายไฟไว้ให้พร้อมครับ

3. Flash Firmware
ต่อไปก็มาลงเฟิร์มแวร์ล่าสุดให้กับอุปกรณ์ของคุณ โดยใช้เครื่องมือ Meshtastic Flasher ซึ่งแนะนำให้ใช้ผ่านเบราว์เซอร์ Chrome จะดีที่สุด ภายในเว็บให้เลือกอุปกรณ์ตามรุ่นที่เราซื้อมา เลือกเวอร์ชันของ firmware เป็นล่าสุด แล้วกด flash ได้เลยครับ
![image![image![image]()](https://image.nostr.build/362c78edcd72da9c5a0bf42d4527788e9a8384441b6199aff2f807dfdf8bcf49.jpg)](https://image.nostr.build/93e348b78ec36153e13aff1141d07ad5b22573a984813b19be82b3530b1199e8.jpg)
4. ติดตั้งแอป Meshtastic
จากนั้นก็ดาวน์โหลดแอป Meshtastic มาลงบนมือถือของคุณได้เลย iPhone: https://meshtastic.org/docs/software/apple/installation/ Android: https://meshtastic.org/docs/software/android/installation/
หลังจากนั้นเชื่อมต่อกับอุปกรณ์ เปิดแอป Meshtastic แล้วเชื่อมต่ออุปกรณ์ LoRa กับมือถือผ่าน Bluetooth ด้วยการกดที่เครื่องหมาย + ที่ขวาล่างในหน้า setting ดังรูป
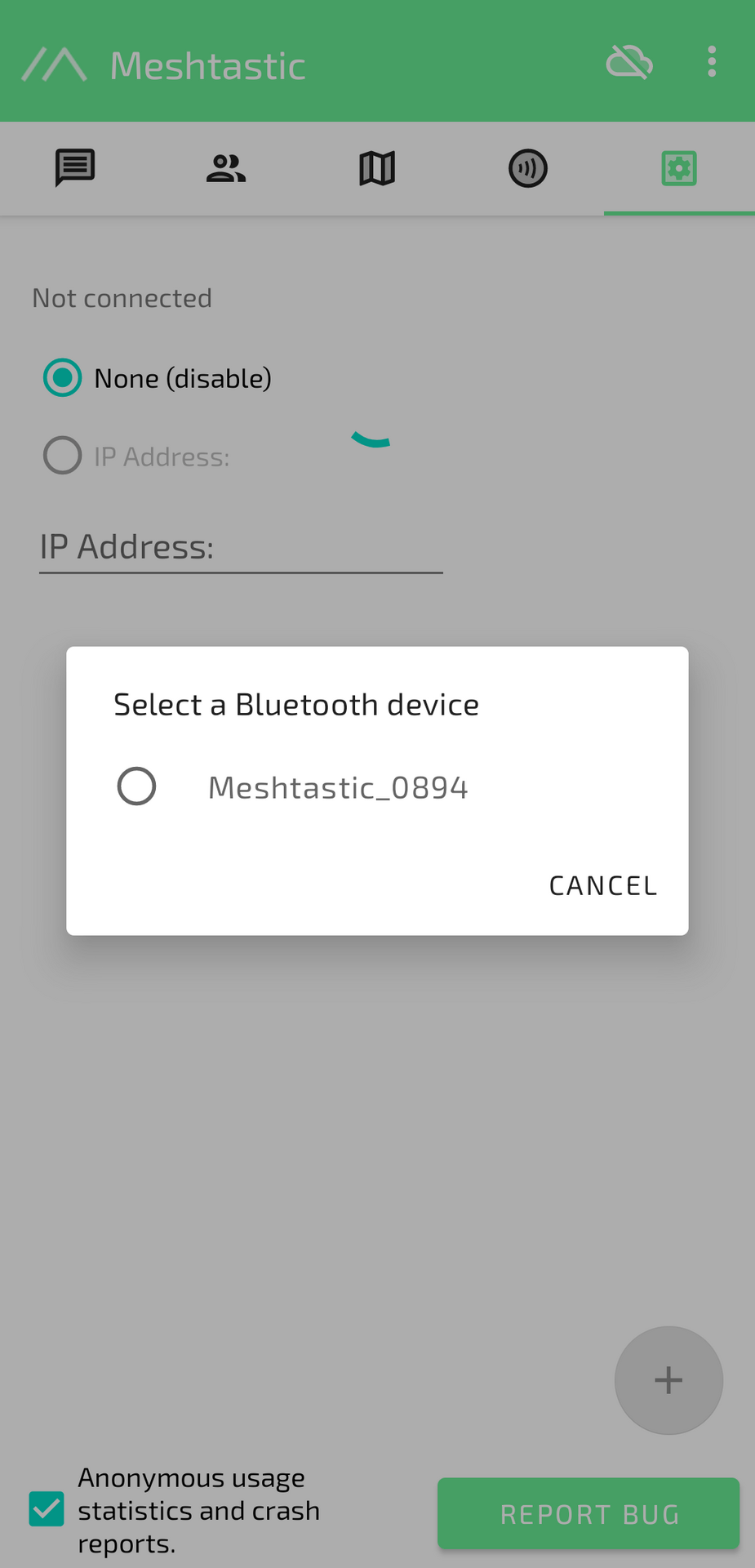 แอปจะทำการค้นหาและเชื่อมต่ออุปกรณ์ ให้ทำการกรอกหมายเลขตามที่ปรากฏบนหน้าจอของอุปกรณ์ lora
แอปจะทำการค้นหาและเชื่อมต่ออุปกรณ์ ให้ทำการกรอกหมายเลขตามที่ปรากฏบนหน้าจอของอุปกรณ์ lora
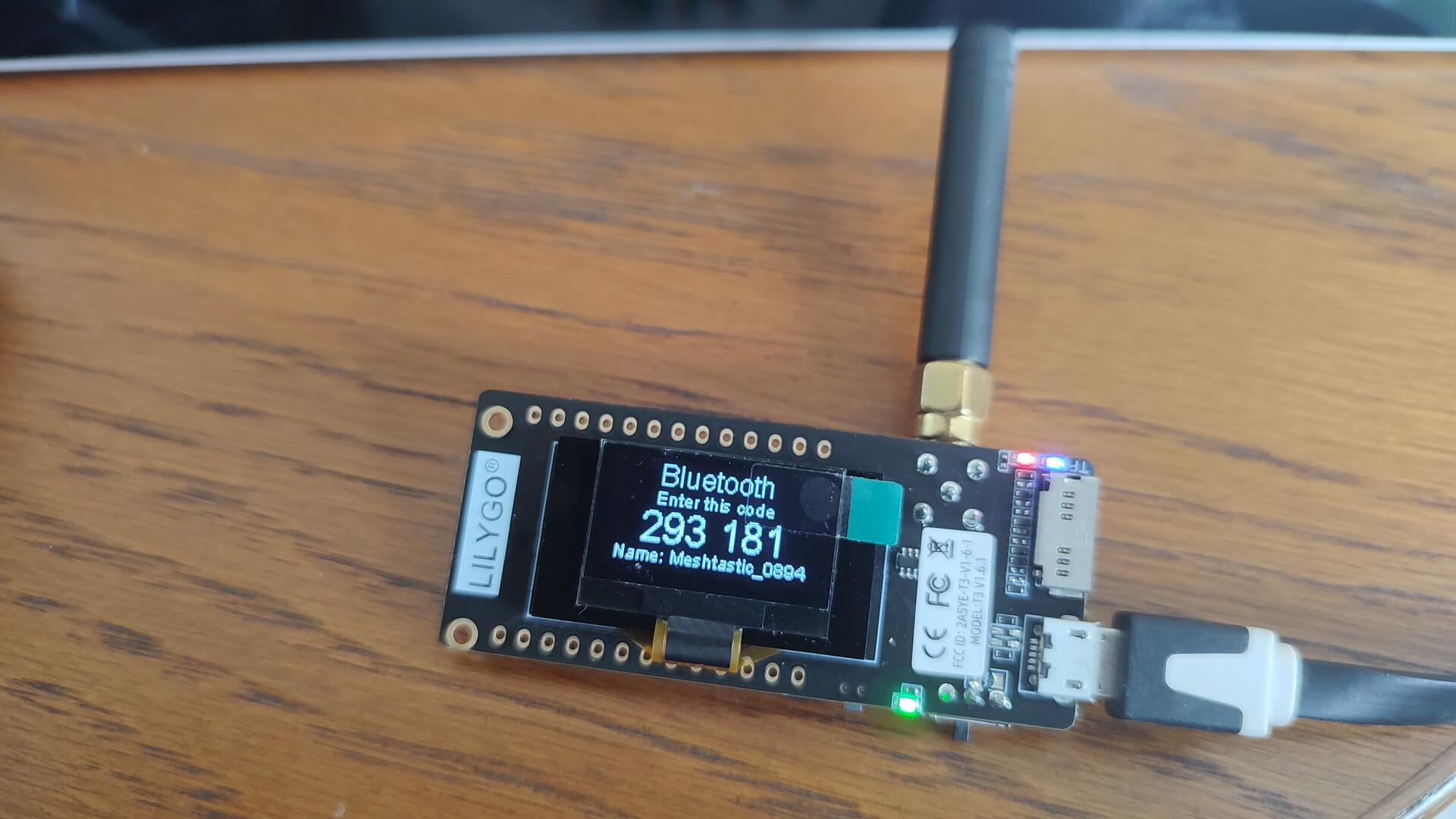
5. ปรับแต่งการตั้งค่า
เข้าไปตั้งค่าในแอป เลือกภูมิภาคตามความถี่ของอุปกรณ์ที่เราซื้อมาครับ ยกตัวอย่างเช่น * ความถี่ 433 MHz ให้เลือก EU_433 * ความถี่ 923 MHz ให้เลือก TH * ความถี่ 2.4 GHz ให้เลือก LORA_24
หลังจากนั้นตั้งชื่ออุปกรณ์ให้เท่ ๆ และปรับแต่งค่าอื่น ๆ ได้ตามใจชอบ
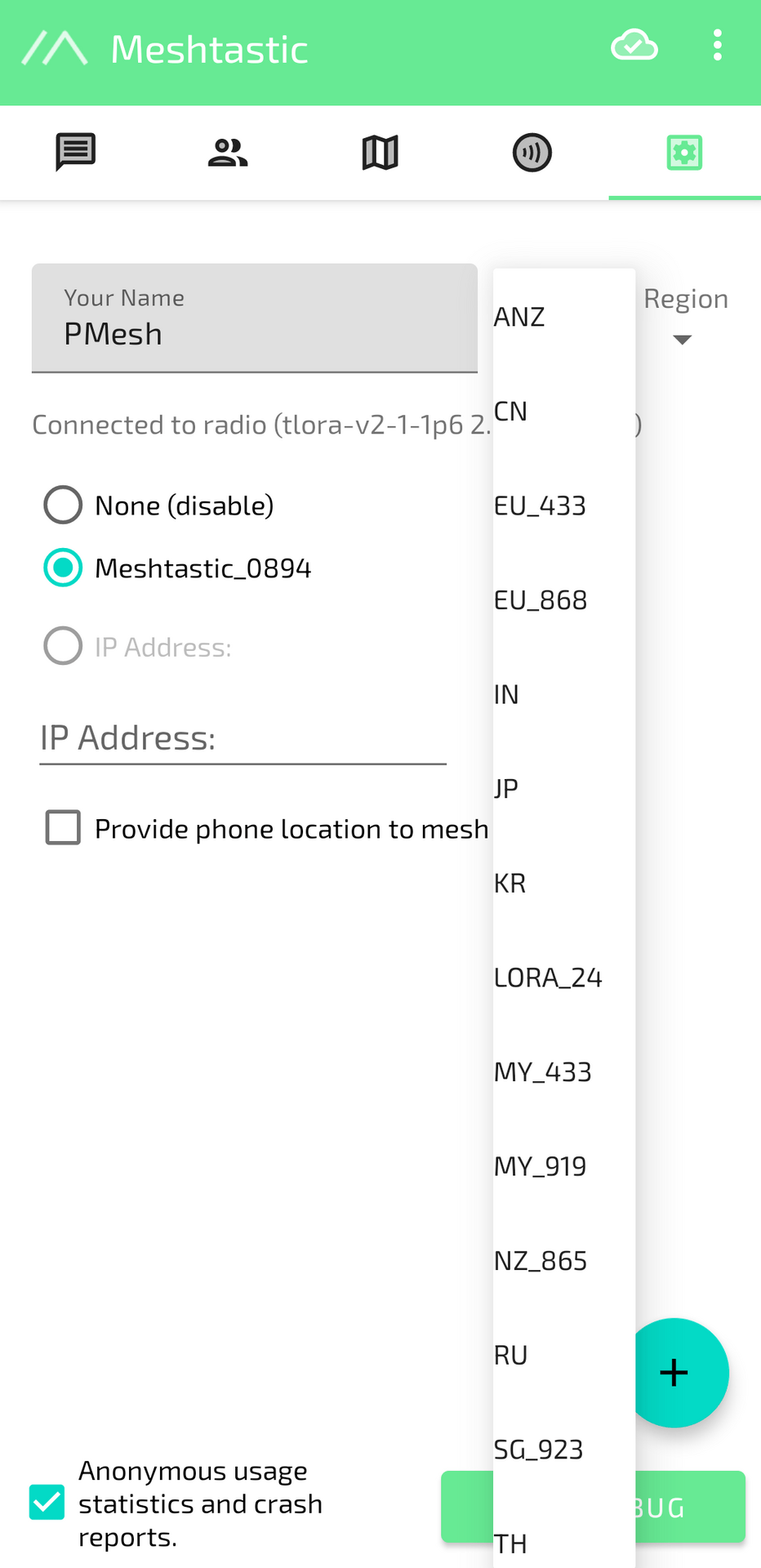
6. ทดสอบส่งข้อความ
ลองส่งข้อความทดสอบไปที่ช่องแชทสาธารณะ "LongFast" ดู แล้วรอคำตอบจากเพื่อน ๆ ในเครือข่าย

7. สนุกกับการสื่อสารแบบไร้ศูนย์กลาง
เมื่อทุกอย่างพร้อมแล้ว ก็เริ่มใช้ Meshtastic ได้เลยครับ ลองสำรวจฟังก์ชันต่าง ๆ และสนุกไปกับการแชทส่วนตัวแบบไม่ต้องพึ่งพาเครือข่ายอินเทอร์เน็ตกันเลยครับ
สรุปส่งท้าย
Meshtastic เป็นโซลูชันการสื่อสารที่ดีและประหยัดสุด ๆ เหมาะกับการใช้ในพื้นที่ที่ไม่มีสัญญาณโทรศัพท์หรืออินเทอร์เน็ต เพราะมันทำงานได้โดยไม่ต้องพึ่งพาโครงสร้างพื้นฐานของเครือข่ายที่รัฐควบคุม เพื่อน ๆ สามารถใช้ Meshtastic ได้อย่างอิสระ ใครได้ลองกันแล้วเป็นยังไงก็อย่าลืมทักกันเข้ามานะครับ จะ DM ผ่าน meshtatic นี้หรือ nostr ก็ได้ หากเพื่อน ๆ มีข้อสงสัยหรือติดปัญหาอะไรก็ทักมาถามกันได้ ไว้พบกันใหม่นะครับ :)
-
 @ e83b66a8:b0526c2b
2024-09-21 16:29:23
@ e83b66a8:b0526c2b
2024-09-21 16:29:23Here are some of the more interesting projects that I like:
Messaging:
https://www.0xchat.com/#/ - Private messaging - think WhatsApp
Xitter Like Clients:
https://damus.io/ - iPhone client
https://nostrapps.com/amethyst - Android client
https://primal.net/downloads - Android, iPhone & Desktop
https://shipyard.pub/posts - Schedule future posts
Interesting sites:
https://zap.stream/ - Video streaming
https://fountain.fm/ - Podcasting
https://wavlake.com/ - Music streaming
https://shopstr.store/ - Online shop
https://zap.cooking/recent - Cooking recipes
https://ostrich.work/ - NOSTR jobs board
NOSTR tools
https://nostr.band/ - Powerful search tool
https://nostr.wine/ - Powerful, but centralised paid relay
https://npub.pro/ - Website creation tool
https://nostr.build/ - Media and file storage
https://relay.tools/ - Build and curate your own relay
https://creatr.nostr.wine/subscriptions/new-user - Creator tools
List of NOSTR apps:
https://nostrapps.com/
-
 @ 4ba8e86d:89d32de4
2024-10-25 11:06:58
@ 4ba8e86d:89d32de4
2024-10-25 11:06:58Ele se concentra em fornecer uma experiência de usuário aprimorada, mantendo a liberdade e o controle do usuário sobre seu dispositivo.
O projeto LineageOS foi iniciado em 2016, quando o desenvolvimento do CyanogenMod, uma ROM personalizada popular, foi interrompido. Uma comunidade dedicada de desenvolvedores e entusiastas do Android se uniu para criar o LineageOS como uma continuação do CyanogenMod.
Uma das principais características do LineageOS é a capacidade de personalizar e ajustar o sistema operacional de acordo com as preferências do usuário. Ele oferece uma ampla gama de opções de personalização, permitindo que os usuários alterem a aparência, o comportamento e os recursos do sistema de acordo com suas necessidades.
Além da personalização, o LineageOS também se concentra na segurança e privacidade dos usuários. Ele fornece atualizações regulares de segurança para corrigir vulnerabilidades e proteger os dispositivos contra ameaças. Além disso, o LineageOS oferece controle granular sobre as permissões de aplicativos, permitindo que os usuários decidam quais permissões um aplicativo pode acessar.
O LineageOS também é conhecido por estender o ciclo de vida de dispositivos mais antigos, fornecendo suporte para modelos mais antigos que não recebem mais atualizações oficiais do fabricante. Isso permite que os usuários continuem usando seus dispositivos com um sistema operacional atualizado e seguro.
O projeto LineageOS é impulsionado pela comunidade e mantido por uma equipe de desenvolvedores voluntários. A comunidade é ativa e colaborativa, fornecendo suporte, solução de problemas e contribuições para melhorar o sistema operacional.
O LineageOS oferece aos usuários de dispositivos Android uma opção alternativa, personalizável e segura em relação ao sistema operacional padrão. Com sua ênfase na personalização, segurança e suporte a dispositivos mais antigos, o LineageOS atrai uma base de usuários dedicada que valoriza a liberdade e o controle sobre seus dispositivos.
Obtenha o LineageOS agora! LineageOS, uma distribuição Android de código aberto, está disponível para vários dispositivos, com mais sendo continuamente adicionados graças à maior e crescente comunidade de código aberto Android. Junte-se a nós e dê nova vida ao seu dispositivo, seja ele antigo ou novo.
https://wiki.lineageos.org/devices/
Lista disponivel
Google Pixel Samsung Xiaomi Motorola LG ASUS Lenovo OnePlus Sony Nokia ZUK Banana Pi BQ Dynalink Essential F(x)tec Fairphone HardKernel LeEco 10.or Nextbit Nothing Nubia NVIDIA Radxa Razer SHIFT
Xiaomi: - Xiaomi 11 Lite 5G NE (AKAXiaomi 11 Lite NE 5GMi 11 LE) - Mi 10T (AKAMi 10T ProRedmi K30S Ultra) - Mi 10T Lite (AKAMi 10iRedmi Note 9 Pro 5G) - Mi 11 Lite 5G (renoir) - Mi 11 Pro (mars) - Mi 11i (AKARedmi K40 ProRedmi K40 Pro+Mi 11X Pro) - Mi 5 (gemini) - Mi 5s Plus (natrium) - Mi 6 (sagit) - Mi 8 (dipper) - Mi 8 Explorer Edition (ursa) - Mi 8 Pro (equuleus) - Mi 8 SE (xmsirius) - Mi 9 SE (grus) - Mi 9T (AKARedmi K20 (China)Redmi K20 (India)) - Mi A1 (tissot) - Mi CC 9 (AKAMi 9 Lite) - Mi CC9 Meitu Edition (vela) - Mi MIX 2 (chiron) - Mi MIX 2S (polaris) - Poco F1 (beryllium) - POCO F2 Pro (AKARedmi K30 ProRedmi K30 Pro Zoom Edition) - POCO F3 (AKARedmi K40Mi 11X alioth) - POCO M2 Pro (AKARedmi Note 9SRedmi Note 9 Pro (Global)Redmi Note 9 Pro (India)Redmi Note 9 Pro MaxRedmi Note 10 Lite miatoll) - POCO X3 NFC (surya) - POCO X3 Pro (vayu) - Redmi 3S (AKARedmi 3XRedmi 4 (India)Redmi 4XRedmi Note 5A PrimeRedmi Y1 Prime Mi8937) - Redmi 4A (AKARedmi 5ARedmi Note 5A LiteRedmi Y1 Lite Mi8917) - Redmi 7 (AKARedmi Y3 onclite) - Redmi 7A (AKARedmi 8Redmi 8ARedmi 8A Dual Mi439)
- Redmi 9 (lancelot)
- Redmi Note 10 Pro (AKARedmi Note 10 Pro (India)Redmi Note 10 Pro Max (India) sweet)
- Redmi Note 10S (AKARedmi Note 10S NFCRedmi Note 10S Latin America rosemary)
- Redmi Note 7 Pro (violet)
- Redmi Note 8 (AKARedmi Note 8T ginkgo)
- Redmi Note 9 (merlinx)
LG: - G5 (International) (h850) - G5 (T-Mobile) (h830) - G5 (US Unlocked) (rs988) - G6 (EU Unlocked) (h870) - G6 (T-Mobile) (h872) - G6 (US Unlocked) (us997) - V20 (AT&T) (h910) - V20 (Global) (h990) - V20 (GSM Unlocked - DirtySanta) (us996d) - V20 (GSM Unlocked) (us996) - V20 (Sprint) (ls997) - V20 (T-Mobile) (h918) - V20 (Verizon) (vs995) - V30 (T-Mobile) (h932) - V30 (Unlocked) (joan)
Motorola: - edge (racer) - edge 20 (berlin) - edge 20 pro (pstar) - edge 2021 (berlna) - edge 30 (dubai) - edge s (AKAmoto g100 nio) - moto e5 plus (XT1924-1/2/4/5) (rhannah) - moto e5 plus (XT1924-3/9) (ahannah) - moto e5 plus (XT1924-6/7/8) (hannah) - moto g 5G (AKAmoto one 5G ace kiev) - moto g 5G plus (AKAmoto one 5G nairo) - moto g200 5G (AKAEdge S30 xpeng) - moto g32 (devon) - moto g42 (hawao) - moto g5 (cedric) - moto g52 (rhode) - moto g5s (montana) - moto g6 plus (evert) - moto g7 (river) - moto g7 play (channel) - moto g7 plus (lake) - moto g7 power (ocean) - moto x (2014) (victara) - moto x4 (payton) - moto z (griffin) - moto z play (addison) - moto z2 force (nash) - moto z2 play (albus) - moto z3 (messi) - moto z3 play (beckham) - one action (troika) - one fusion+ (liber) - one power (chef) - one vision (AKAp50 kane) - one zoom (parker)
Google: - ADT-3 (deadpool) - Nexus 6 (shamu) - Nexus 7 2013 (LTE, Repartitioned) (debx) - Nexus 7 2013 (Wi-Fi, Repartitioned) (flox) - Pixel (sailfish) - Pixel 2 (walleye) - Pixel 2 XL (taimen) - Pixel 3 (blueline) - Pixel 3 XL (crosshatch) - Pixel 3a (sargo) - Pixel 3a XL (bonito) - Pixel 4 (flame) - Pixel 4 XL (coral) - Pixel 4a (sunfish) - Pixel 4a 5G (bramble) - Pixel 5 (redfin) - Pixel 5a (barbet) - Pixel 6 (oriole) - Pixel 6 Pro (raven) - Pixel 6a (bluejay) - Pixel 7 (panther) - Pixel 7 Pro (cheetah) - Pixel 7a (lynx) - Pixel tablet - Pixel XL
Samsung: - Galaxy S4 (SCH-R970, SPH-L720) - jfltespr - Galaxy S4 (SGH-I337) - jflteatt - Galaxy S4 Active - jactivelte - Galaxy S4 Value Edition (GT-I9515/L) - jfvelte - Galaxy S5 Active (G870F) - klteactivexx - Galaxy S5 LTE (G9006V/8V) - kltechn - Galaxy S5 LTE (G900AZ/S902L) - klteaio - Galaxy S5 LTE (G900F/M/R4/R7/T/V/W8) - klte - Galaxy S5 LTE (G900I/P) - kltedv - Galaxy S5 LTE (G900K/L/S) - kltekor
- Galaxy S5 LTE (SC-04F/SCL23) - kltekdi
- Galaxy S5 LTE Duos (G9006W/8W) - kltechnduo
- Galaxy S5 LTE Duos (G900FD/MD) - klteduos
- Galaxy S9 - starlte
- Galaxy S9+ - star2lte
- Galaxy Tab A 8.0 (2019) - gtowifi
- Galaxy Tab S5e (LTE) - gts4lv
- Galaxy Tab S5e (Wi-Fi) - gts4lvwifi
- Galaxy Tab S6 Lite (LTE) - gta4xl
- Galaxy Tab S6 Lite (Wi-Fi) - gta4xlwifi
https://lineageos.org/
https://github.com/lineageos
-
 @ eac63075:b4988b48
2024-09-20 09:23:23
@ eac63075:b4988b48
2024-09-20 09:23:23Overview of the Infrastructure
- Umbrel/Citadel/RaspiBlitz/Start9 Server
- Purpose: Acts as your personal Bitcoin and Lightning Network node.
- Setup: Installed on a Raspberry Pi 4 running Debian or Umbrel OS.
- Benefits:
- Participate in Bitcoin Consensus: Validates transactions and blocks independently.
- Lightning Network Routing: Facilitates faster transactions and earns routing fees.
- Cold Storage Wallets
- Coldcard: A highly secure hardware wallet designed specifically for Bitcoin.
- Ledger Nano X: A versatile hardware wallet supporting multiple cryptocurrencies.
- Purpose: Store your Bitcoin offline to protect against online threats.
- Secure Devices
- Encrypted Computer: A notebook with encrypted storage for managing your wallets and nodes securely.
- Android Phone with Secure Area:
- Old Device: Repurposed without a SIM card to minimize exposure.
- Secure Area for Apps: Uses features like Samsung's Secure Folder/Knox to isolate sensitive applications.
- NerdMiner
- Purpose: A compact mining device like the Nerdminer V2 to engage in Bitcoin mining.
- Function: Attempts to mine Bitcoin blocks, offering a chance (albeit very low) to earn block rewards and learn about the mining process.
 ### Advantages of This Setup
### Advantages of This Setup- Self-Sovereignty: You have complete control over your funds without relying on third-party services.
- Enhanced Privacy:
- CoinJoin Transactions: Mix your coins with others to obfuscate transaction history.
- No SIM Card Devices: Reduces the risk of SIM swapping attacks.
- Network Participation:
- Consensus Involvement: By running a full node, you help maintain the network's integrity.
- Lightning Network: Improve transaction speeds and network scalability.
- Security:
- Cold Storage: Keeps your private keys offline, away from potential online threats.
- Encrypted Devices: Protects data even if physical devices are lost or stolen.
 ### Simplifying the Perceived Complexity
### Simplifying the Perceived ComplexityWhile the infrastructure may seem daunting, it's more approachable than it appears:
- Starting Point: Use an old computer or phone as a cold wallet with software like Electrum or Sparrow.
- Step-by-Step Setup:
- Begin with setting up the Umbrel/Citadel/RaspiBlitz/Start9 server.
- Gradually add hardware wallets like Coldcard, SeedSigner DIY, Jade, Ledger, Trezor or Onekey.
- Implement security measures on your existing devices.
- Community Resources: Numerous guides and communities are available to assist with each step.
 ### Embracing Freedom and Privacy
### Embracing Freedom and PrivacyPracticing self-sovereignty and custody isn't just about securing your Bitcoin—it's about embracing freedom and privacy in the digital age. By taking control:
- Financial Independence: You're not dependent on banks or exchanges.
- Data Privacy: Your financial data remains confidential.
- Empowerment: Gain a deeper understanding of how Bitcoin and blockchain technology work.
Remember: Even simple steps like using an old device as a cold wallet can significantly enhance your security. The journey towards complete self-sovereignty is a progressive one, and each step you take strengthens your position in the digital world.
-
 @ 8f69ac99:4f92f5fd
2024-10-25 09:49:56
@ 8f69ac99:4f92f5fd
2024-10-25 09:49:56O recente relatório do Banco Central Europeu, As Consequências Distribucionais do Bitcoin, recicla a velha narrativa de que o Bitcoin é um activo especulactivo que causa desigualdade de riqueza sem oferecer benefícios económicos tangíveis. Os autores, Ulrich Bindseil e Jürgen Schaaf, desfilam as críticas de sempre, afirmando que o Bitcoin falhou como sistema de pagamento global e que se transformou numa bolha, enriquecendo os primeiros utilizadores à custa da sociedade. Também lançam uma pitada de alarmismo ambiental e argumentam que o Bitcoin ameaça a democracia.
Como era de esperar, o BCE continua apegado às mesmas concepções erradas que já foram desmentidas inúmeras vezes. O que este relatório não percebe, de forma espectacular, é que o Bitcoin não é apenas mais um activo; é uma tábua de salvação para aqueles desiludidos com os sistemas fiduciários inflacionários e governos corruptos. Ao longo desta análise, vamos desmontar os argumentos do BCE, expondo não só o seu profundo desconhecimento sobre o Bitcoin, mas também a ignorância gritante em relação ao seu potencial de conceder soberania financeira a milhões de pessoas em todo o mundo. O BCE retrata o Bitcoin como uma ferramenta elitista, mas ignora como as suas próprias políticas têm sistematicamente enriquecido alguns poucos à custa da maioria. Vamos então entrar no assunto.
1. Deturpam o Papel do Bitcoin como Sistema de Pagamentos
"O Bitcoin nunca foi usado em grande escala para transacções legais no mundo real."
Que originalidade. Os autores descartam a utilidade de pagamento do Bitcoin com um gesto, mostrando que não compreendem a Lightning Network, que facilita transacções rápidas, baratas e escaláveis a nível global. Certamente, talvez os europeus ainda não estejam a comprar os seus cafés com Bitcoin, mas isso é irrelevante. O Bitcoin é uma tábua de salvação financeira em locais como El Salvador e em inúmeras outras regiões que sofrem com sistemas fiduciários em colapso.
Esta visão eurocêntrica, como se todo o mundo partilhasse das mesmas condições económicas, reflecte uma total falta de perspectiva. Os autores seleccionam dados a dedo para encaixar na sua narrativa anti-Bitcoin, enquanto convenientemente ignoram os milhões que utilizam o Bitcoin para escapar à hiperinflação e a regimes autoritários. A afirmação de que o Bitcoin não é usado para transacções "legais" é não só enganosa, como revela a sua ignorância sobre as necessidades reais de quem vive fora da sua bolha privilegiada.
2. Deturpam o Bitcoin como activo Especulactivo
"O Bitcoin não gera qualquer fluxo de caixa (como o imobiliário), juros (como as obrigações) ou dividendos (como as ações)."
Parabéns, BCE, acabaram de perder o ponto fulcral do Bitcoin. Esta afirmação mostra uma falta de entendimento fundamental do que torna o Bitcoin único. Ao contrário de imóveis ou obrigações, o Bitcoin é uma forma alternativa de dinheiro—não algum esquema de rendimento passivo.
O valor do Bitcoin não depende de gerar dividendos ou juros, mas advém da sua escassez, descentralização e resistência à censura. Ao reduzir o Bitcoin a modelos de activos tradicionais, o BCE ignora o paradigma económico revolucionário que este oferece: uma escapatória aos sistemas fiduciários inflacionários, particularmente para os milhares de milhões de pessoas presas em sistemas financeiros corruptos.
Ao tentar enquadrar o Bitcoin em modelos convencionais, os autores revelam a sua preguiça intelectual. A utilidade do Bitcoin reside no seu potencial como dinheiro sólido, e não como um veículo de investimento para especuladores atrás de rendimento.
3. Deturpam os Custos Ambientais e Sociais da Mineração
"A mineração de Bitcoin consome muita energia e causa danos ecológicos e sociais."
Ah sim, o argumento gasto sobre o consumo energético. Enquanto a mineração de Bitcoin realmente requer energia, os autores omitem convenientemente os enormes avanços que a indústria fez em direcção à sustentabilidade. Cada vez mais, os mineradores de Bitcoin recorrem a fontes de energia renovável e, em alguns casos, estão até a ajudar a financiar infraestruturas de energia verde.
A ironia aqui é que o BCE, uma instituição que fomenta políticas que inflam bolhas imobiliárias e de acções, de repente está preocupado com os custos sociais e ambientais. E mais, ignoram como a procura de energia barata por parte do Bitcoin incentiva realmente o desenvolvimento de soluções energéticas sustentáveis. Num mundo onde os sistemas fiduciários alimentam a ganância corporativa e a degradação ambiental, o Bitcoin está posicionado para impulsionar uma verdadeira inovação na energia verde.
4. Visão Deturpada da Redistribuição de Riqueza
"Os efeitos de riqueza do Bitcoin beneficiam os primeiros utilizadores à custa dos que chegam mais tarde e dos que não o possuem."
Isto é pura comédia. Aparentemente, o BCE acabou de descobrir que os primeiros investidores em qualquer activo beneficiam mais do que os que chegam depois. Não é assim que os mercados funcionam? Os primeiros investidores em acções, imóveis e ouro beneficiam de forma desproporcional—mas, curiosamente, isto só se torna um problema quando se trata de Bitcoin.
O que o BCE realmente teme é que o Bitcoin democratize a riqueza de uma maneira que eles não conseguem controlar. Com o Bitcoin, não precisas de acesso privilegiado para participar. Não precisas de um corretor XPTO ou de permissão dos guardiões financeiros. Ao contrário das próprias políticas do BCE—concebidas para inflacionar a riqueza dos já ricos através de bolhas imobiliárias e do mercado de acções—Bitcoin oferece um campo de jogo nivelado para qualquer pessoa com uma ligação à internet.
5. Sensacionalismo: a Ameaça à Democracia
"O aumento perpétuo do preço do Bitcoin empobrece o resto da sociedade e põe em risco a democracia."
Aqui, os autores entram no melodrama, avisando que o aumento do preço do Bitcoin põe em risco a democracia. É fascinante como ignoram a verdadeira ameaça à democracia: as suas próprias políticas inflacionárias.
Na realidade, os sistemas fiduciários, através da inflação incessante e do quantitative easing, erodem sistematicamente a riqueza dos mais pobres e da classe média. Os ricos, com as suas carteiras de acções e imóveis, conseguem resistir à tempestade. Mas o trabalhador comum, cujo salário compra cada vez menos a cada ano, é esmagado. Se há algo que ameaça a democracia, é o poder descontrolado do BCE de desvalorizar a moeda que as pessoas usam para viver. Bitcoin, por outro lado, dá às pessoas uma reserva de valor incorruptível e descentralizada, imune aos caprichos dos banqueiros centrais.
6. Percepção "Equivocada" da Escalabilidade do Bitcoin
"As transações em Bitcoin na blockchain são lentas e caras."
Esta crítica ignora a realidade do progresso tecnológico. As transacções on-chain de Bitcoin nunca foram pensadas para compras diárias—para isso é que serve a Lightning Network. Os autores agarram-se a esta crítica desactualizada, como se o Bitcoin fosse uma entidade estática que não evoluiu na última década.
Soluções de segunda camada como a Lightning Network permitem transacções quase instantâneas e de baixo custo, tornando o Bitcoin escalável de maneiras que o BCE se recusa a reconhecer. Mas porque deixar que os factos estraguem uma boa história de medo?
7. Ignoram o Impacto Económico Global do Bitcoin
"O Bitcoin não tem casos de uso benéficos para a sociedade."
Esta afirmação é tão limitada que é quase impressionante. A utilidade do Bitcoin não se trata de conveniência para os ocidentais comprarem café; trata-se de sobrevivência para as pessoas em países como a Venezuela, o Líbano ou a Nigéria.
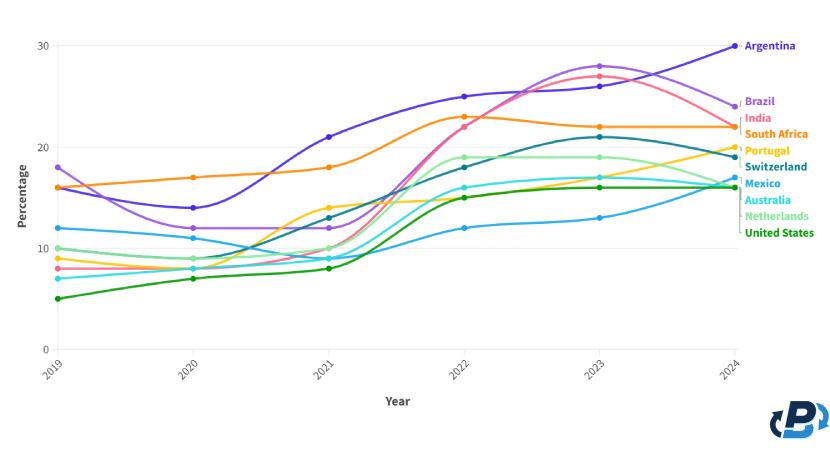
Quando as moedas locais colapsam e as pessoas não podem confiar nos seus bancos, o Bitcoin oferece uma saída. Ao descartar o impacto real de Bitcoin sobre os milhares de milhões (mais de metade da população mundial) de pessoas que vivem sob regimes opressivos e em hiperinflação, o BCE revela um embaraçoso viés ocidental e falta de empatia. O Bitcoin é mais do que apenas um activo alternativo, é uma tábua de salvação para pessoas em todo o mundo que sofrem com sistemas fiduciários falhados.
Conclusão
O relatório do BCE recicla críticas desactualizadas e já desmentidas, não conseguindo ver o panorama geral. Aplica modelos financeiros antigos a uma nova forma de dinheiro, ignorando o potencial de Bitcoin para democratizar o acesso a um sistema financeiro justo, descentralizado e incorruptível. Enquanto os bancos centrais, como o BCE, continuam a desvalorizar moedas e a inflacionar bolhas de activos (e parece que vem ai mais...), Bitcoin oferece às pessoas um caminho para a soberania financeira.
O verdadeiro valor de Bitcoin não se encontra nas críticas superficiais e eurocêntricas do BCE. O seu valor reside na capacidade de fornecer liberdade financeira a indivíduos em todo o mundo, libertos da má gestão de governantes e banqueiros centrais. Se há algo que ameaça a democracia, é o historial do BCE de enriquecer alguns poucos à custa de muitos. Bitcoin, por outro lado, oferece um futuro mais justo—um onde são os indivíduos, e não as instituições, que têm o poder.
Alguma literatura: - Universidade de Cornell - Bitcoin pode impulsionar o desenvolvimento de energias renovaveis - Aldeias em Africa com electricidade atraves de Bitcoin - Relatorio de 2023 sobre a Lightning Network da River - Adopcao de Bitcoin por Pais
Photo by Taras Chernus on Unsplash
Bitcoin #BCE
-
 @ 502ab02a:a2860397
2024-09-20 02:30:23
@ 502ab02a:a2860397
2024-09-20 02:30:23
มีเรื่องจะประกาศครับ ถ้าสามารถแชร์ออกไปได้ก็ยินดีมากครับ
เป็นความตั้งใจตั้งแต่ก่อนงาน Thailand Bitcoin Conference 2024 ว่าจะเป็นงานสุดท้ายที่ผมจะใช้คำว่า ขนมคีโต
ตลอดเส้นทางที่ผ่านมา หมวกอีกใบนึงของผมคือ การถ่ายทอดความรู้ที่ศึกษามาในแขนงโภชนาการ และคำถามตลอดกาลคือ "อันไหนเป็นอาหารคีโต"
จริงอยู่ครับก็ยินดีตอบให้ได้ แต่ลึกๆมันก็มีความขุ่นๆนิดๆว่า หากเป็นขวบปีแรกของคีโตก็ยังพอเข้าใจ แต่ขณะนี้ก้าวเข้าวปีที่ 8 แล้ว อีกไม่เท่าไรก็ 10ปีคีโตในไทยแล้ว สิ่งแรกที่คนคีโตมองหาเวลาซื้ออาหารคือ ฉลากคีโต
แล้วพอเจอบางสินค้าแปะป้ายคีโต แต่มีวัตถุดิบที่ต่างจากกูรูต่างจากเจ้าพ่อเจ้าแม่คีโต ได้บัญญัติไว้ ก็เกิดความสับสนวุ่นวายทะเลาะเบาะแว้ง ว่าตกลงมันเป็นอาหารคีโตหรือไม่
ผมเลือกทางนี้ครับ หักดิบไปเลย
ต่อไปนี้ผมจะไม่ใส่คำว่า คีโต ในชื่อเรียกอาหาร ต่อไปนี้จะไม่มีชีสเค้กคีโต ดาร์คชอคกานาซคีโต หน้าไก่คีโต บลาบลาบลา ที่มีคีโตเป็นชื่อเรียก อีกต่อไปครับ พอกันทีกับสิ่งนี้
ของกินทุกอย่างที่ผมทำ จะใช้ความเชี่ยวชาญด้านโภชนาการ ความสะอาด สุขอนามัย ฉลากสารอาหาร ใช้การคำนวนแบบเผื่อข้อผิดพลาด(บวก ไม่ลบ) ด้วยการใส่ Macro Nutrient ให้ในทุกเมนู !!!!
เพราะผมเชื่อว่า การกินคาร์บต่ำ เป็นการกินแบบ "ปกติ" การกินคาร์บมากก็เป็นการกินแบบ "ปกติ" เหมือนคนไม่ชอบกินผิก ไม่ชอบกินปลา ไม่ชอบกินเนื้อ อันนี้มันก็แค่คนไม่ชอบกินคาร์บสูงเกินไป แค่นั้นครับ เป็นการกินแบบปกติ ย้ำ เป็นการกินแบบปกติ คาร์บต่ำแบบคีโต เป็นการกินแบบปกติ ที่ควรเป็นมานานแล้วด้วย
การยัดทะนานคาร์บสูงมากๆ ในมุมมองผมคือ นี่แหละที่ไม่ปกติ
ทีนี้ความไม่ปกตินี้มันก็ไม่ผิดอะไรด้วย ถ้าคนกินไม่ปกติ นิยามไม่ปกติคือ ไม่ใช่คนทั่วๆไปเช่น นักกล้าม นักกีฬา ผู้ที่ใช้ "พลังงาน" สูงมากๆแลละต้องการใช้คาร์บ เพื่อการใดการหนึ่งโดยเฉพาะ ดังนั้นไม่มีอะไรที่ผิดเลยครับ ใครอยากกินอะไร กิน ตราบใดที่เรารู้ตัวเราเองว่าทำอะไร
ผมอยู่ในวงการธุรกิจทั้งอาหารและการโฆษณา เข้าใจดีครับว่าการแปะป้ายคีโต คือการช่วยให้คนตัดสินใจง่ายขึ้น เข้าใจง่ายขึ้น ช่วยในการขายให้สะดวกขึ้น แต่ ผมพอแล้วครับ เหรียญอีกด้านนึงของป้ายนีคือ มันไม่ได้ช่วยให้คนคีโต เรียนรู้การทำความเข้าใจด้านสารอาหารเท่าที่ผมคาดหวัง เพราะถ้าไม่มีป้ายพวกนี้ คนคีโตหลายๆคนถึงกับไปไม่เป็นกันเลยทีเดียว แล้วทุกวันนี้เหรียญมันออกด้านนี้ซะเยอะด้วย
นอกจากนี้ประเด็นที่หลีกไม่ได้คือ การหมอบคลานเข้ารับวัตถุดิบคีโตจากกูรู ซึ่งไม่เคยได้เหตุผลในการ "ห้าม" ของหลายๆอย่างเช่น สารหวานบางประเภท แครอท ฟักทอง(ตัวนี้มีคนถามและส่งมาให้ดูเยอะ เดี๋ยวจัดให้เคลียร์ๆ)
ซึ่งใครที่เลือกกินสิ่งนี้แล้วแชร์ความรู้ให้คนคีโตว่ากินได้ ก็จะโดนตรรกะวิบัติจากกูรูด้วยการแปะคำว่า "อยากกิน เลยชวนคนอื่นกิน ชวนคนให้ไม่เคร่ง" เป็นตรรกะวิบัติที่เรียกว่า Ad Hominem หรือ การโจมตีที่ตัวบุคคล นั่นเอง (ref : https://siripun.com/2023/06/09/logical-fallacies-2-ad-hominem ) ทั้งที่ถ้าจะนิยามคำว่าเคร่ง สิ่งที่กูรูให้ทำ ไม่สามารถมีคำตอบที่สร้างสมการสมดุลได้ (ทำไม A ได้แล้ว B ไม่ได้ถ้าเทียบบริบทเอามาชนกันชัดๆเลย)
จริงๆก็อยากรณรงค์ให้ผู้ประกอบการอาหารคีโต ร่วมโครงการนี้ แต่เข้าใจว่ามันคงไม่สามารถทำได้ เพราะอาจจะมองในมุมที่ต่างกัน ผมเข้าใจในสิ่งนั้นครับ แต่มุมของผมคือ การทำอาหารคีโตให้กลับมาอยู่ในประเภทอาหารปกติ จะยิ่งขยายมูลค่าตลาดออกไปได้มากกว่าทุกวันนี้
ตลาดคีโตมันซบเซา เพราะเราทำให้มัน "ประหลาด" ทำให้มันกลายเป็นของ "ไม่ปกติ" พอได้น้ำหนัก หุ่น ลูก สมปรารถนาแล้วก็ถวิลหาการ "ออกไปกินปกติ" นั่นคือการทำให้ตลาดหายไปเรื่อยๆเพราะพวกคุณเองครับ ผมกลับมองว่าทำให้คีโตคืออาหารปกติ แล้วกินกันไปตลอด ไม่มีการขอออกจากเผ่า หานเป็ดอะไรคือทางที่ดีกว่า ได้สุขภาพที่ดีกว่า
คีโตคือการกินปกติ ไม่ควรต้องมาแยกเป็นชนเผ่าอะไรเลย คีโตคือคนเมือง คนมีความรู้ คือ วิทยาศาสตร์ คือความฉลาดในการเลือกสารอาหาร อย่าไปยัดเยียดความ "ไม่ปกติ" ให้อาหาร "ปกติ"
ก็เลยคิดว่า ไม่เป็นไร ร้านคีโตร้านใดอยากร่วมเรายินดี แต่ถ้ามองว่าไม่เอาด้วยก็ยินดีเหมือนกัน เพราะการค้าเสรี อยากทำอะไรก็ทำได้ครับ ในส่วนตัวผม เราทำของเรา เราเริ่มของเราเลยก็ได้ เพราะเส้นทางที่ผ่านมา เราก็เดินอยู่ในเส้นทางของเราอยู่แล้ว และผมเชื่อใน Proof of Work ครับ ผมสามารถทุ่มแรงกายแรงใจ ลงในอาหาร ลงในการสอน ให้คนตระหนักถึง "สารอาหาร" มากกว่า "ป้ายฉลาก"
แล้ววันนึง มันจะส่งผลที่ impact ครับ ผมเชื่ออย่างนั้น Proof of Work สามารถส่งต่อได้ และ พลิกโลกได้ มานับต่อนับแล้ว
ทุกวันนี้ผมทุ่มเนื้อหาด้าน ฉลากอาหาร เพื่อให้คนหัดอ่าน รู้เท่า รู้ทัน มันก็ทำให้ผมยิ่งรู้สึกว่า ผมไม่ควรแปะคำว่าคีโต ลงไปเลย มันเหมือนไปสปอยให้คนลืมพื้นฐานสำคัญ
ไม่ใช่ว่าไม่ง้อคนคีโตนะ คนทำการค้าต้องยินดีกับทุกการค้าอยู่แล้ว แต่ผมกลับมมองว่า ตลาดของผมขอเป็นตลาดที่มีการอ่านฉลาก มีการหัดพิจารณาสารอาหาร ดูคาร์บเป็น เลือกวัตถุดิบที่เหมาะกับแต่ละคน มากกว่าวัตถุดิบที่ต้องได้รับการโปรดจากกูรู
ผมมองว่า คนกินคลีน คนกินไฮโปรตีน หรือแม้แต่แค่คนที่ไม่อยากกินน้ำตาล ก็จะสามารถกินอาหารที่ผมทำได้ ไม่โดนปิดกั้นจากป้ายคีโต ที่โลกประเคน mind set ให้ว่าต้อง high fat เท่านั้น
ซึ่งถ้าผมทำอาหารในแบบของผม + คนกินพิจารณาได้เองว่าสารอาหารเหมาะกับเขาไหม = การกินแบบมีความรู้จริง เหมาะกับตัวเองจริงๆ
ถือว่าเป็นอีกเส้นทางที่ผมต้อง fight for ครับ ถ้าสำเร็จ มันจะช่วยให้คนในสังคมหลุดกรอบ และมองสารอาหารได้ ดูแลสุขภาพได้ ด้วยพื้นฐานความรู้ที่มากขึ้นครับ ไม่ใช่ทางที่สบายแน่นอนครับ แต่พวกคุณจะได้ประโยชน์ติดตัวไปแน่ๆ
ถามว่าทำเพื่อการค้าใช่ไหม ก็ใช่ครับ การค้ามันคู่กับโลก ผมไม่ค่อยเข้าใจในมุมของการต้องการอะไรฟรีๆอยู่ตลอด ถ้าคุณเคารพใน value แล้วยินดีส่งต่อ value for value คุุณจะยินดีในการค้าที่ไม่ยัดเยียด (fiat) คุณจะยินดีในการส่งต่อ value ด้วยคุณค่า คุณจะยินดีในการมองคุณค่าของ "เวลา" ที่ผู้สร้างผู้ทำลงทุนลงไป (เวลาคือทรัพยการที่มีค่าที่สุดในโลก) แล้วถ้าคุณให้เกียรติกับสิ่งเหล่านี้ คุณจะไม่อยากได้มันฟรีๆ คุณจะกระดากใจที่จะหยิบมันมาเปล่าๆ นี่คือเหตุผลที่ผมไม่เคยมองว่า การทำการค้า มันจะเลวร้ายอะไร แต่ที่แน่ๆ ผมจะไม่ทำ FIAT keto ครับ ผมจะไม่เร่งเร้า ไม่ขู่เข็ญ ไม่ใช้ตรรกะประเภท "ของมันต้องมี" ผมจะแบไต๋แฟร์ๆด้วยสารอาหารครับ
แม้มันจะแลกมาด้วยการขาดโอกาส จากป้าย "คีโต" ก็ตาม แม้คนคีโตจะมองว่า ไม่มีป้ายคือไม่คีโตก็ตาม แม้จะไม่ได้รับการรับรองจากกูรูใดๆ ว่า "คีโตกินได้" ก็ตาม ถ้าจะให้สังคมมีการเรียนรู้สารอาหารขึ้นได้ ผมยอม
pirateketo #ตำรับเอ๋ #siripun #siamstr
-
 @ ee7d2dbe:4a5410b0
2024-10-25 07:25:41
@ ee7d2dbe:4a5410b0
2024-10-25 07:25:41Today, outsourcing and offshoring are integral parts of almost every business strategy, as they help in efficiency and innovation, by continually evolving in response to economic, technological, and geopolitical shifts.
In short, these models not only help to shape your corporate strategies but also influence global labor markets and economies. So, if you are not using them in your business, you are behind the curve.
That’s why in this post, we start with…
A basic understanding of them, Then go over the top 10 differences between outsourcing and offshoring, And lastly, discuss the key factors to keep in mind while choosing between them.
Understanding of Outsourcing & Offshoring
Outsourcing, at its core, means you are hiring third-party services to complete a piece of work or a whole project, which involves delegating specific tasks or services to external companies, often to harness specialized expertise or reduce costs.
For example, Google outsources IT management to firms in India, and Nike outsources manufacturing to factories in Vietnam and China.
Offshoring means you are relocating your business operations to other countries frequently where labor costs are lower like India and China to emphasize geographical cost advantages and talent pools.
For instance, Apple offshores its manufacturing to China, and Wells Fargo offshores customer service to India and the Philippines.
Evolution of Outsourcing
Outsourcing began during the Industrial Revolution in the 18th century when businesses started contracting out non-core activities to outside experts with a view of improving efficiency.
First, it was limited to simple clerical work such as accounting, but, in the late 20th century, outsourcing expanded with the emergence of Business Process Outsourcing (BPO), which also includes more complex service activities such as call center and IT support.
Evolution of Offshoring
Offshoring started to gain momentum in the 1980s and the 1990s due to enhanced telecommunications and the Internet. From then, most developed Western firms started relocating manufacturing and IT services to developing countries like India and China. So, you can mark this era as the start of a new global economy, where geographic boundaries became less relevant to scale businesses.
Outsourcing v/s Offshoring: An In-depth Analysis
As the title suggests, this will be an in-depth analysis of outsourcing vs. offshoring. However, if you are in a hurry and just want to know the differences, please refer to the chart below.
But our recommendation is to go through all the points and understand them thoroughly so you can make the right decision for your company’s future.
Types of Outsourcing and Offshoring
Actually, the types of outsourcing depend on individual perspectives. For instance, HubSpot covers 7 types, PearlTalent covers 9, and Digital Minds BPO covers 11 types of outsourcing in their articles.
Here, we list 4 categories that encompass almost all types:
IT Outsourcing: Hiring top companies, like Agicent, to facilitate IT functions like software development, maintenance, and support.
Business Process Outsourcing (BPO): It is about delegating non-core business processes such as payroll, HR, and customer service.
Source: https://www.agicent.com/blog/outsourcing-vs-offshoring/
-
 @ cb084639:2f16502a
2024-09-17 10:09:23
@ cb084639:2f16502a
2024-09-17 10:09:23รีวิวงาน #TBC2024 สไตล์ #Richter

เรื่องมันเริ่มมาตั้งแต่ช่วงที่ทาง
npub1ejn774qahqmgjsfajawy7634unk88y26yktvwuzp9kfgdeejx9mqdm97a5
ประกาศขายตั๋วงาน TBC2024 และได้ยินมาว่า จะเปิดรับ อาสาสมัครมาช่วยงาน ตั้งแต่วันนั้นก็คิดมาตลอดว่าอยากจะช่วยงานแต่ไม่รู้จะช่วยอะไรดี อย่างน้อยก็ช่วยทำในสิ่งที่ช่วยได้แล้วให้คนที่เราไปแทนได้ไปทำหน้าที่ที่ดีกว่า ก็ถือว่าเป็นการสนับสนุนส่วนหนึ่ง ก็ยังดี เพราะภาพจากปีที่แล้วมันลอยเข้ามา เราเองก็มางานคนเดียวไม่รู้จักใครเลย ได้เห็นพี่นิวและคุณนิ่ม ที่อยู่ร้านขายเสื้อแบบยุ่งมากๆ ถ้ามีคนมาช่วยเพิ่มก็คงดี พอดีเลยที่ทีมงานจับเราลงตำแหน่งนี้ จึงมีโอกาสได้มาช่วยงาน และรู้สึกเป็นเกียรติที่ได้ร่วมงานครับ ขอบคุณทุกคนที่ได้มาเจอกันในงาน ผมอาจจะไม่ได้พูดถึงทุกคนแต่ แค่มองตากันก็เข้าใจแล้ว เจอกันเยอะมากๆ ถ้าใครได้ผ่านร้านขายเสื้อก็จะเจอผมอยู่ตรงนั้น มีเพื่อนๆแวะเวียนมาทักทาย พูดคุย มาป่วน 😄😄 ประโยคที่ส่วนมากจะได้ยินเวลาผมทักทายไม่ใช่ว่าชื่ออะไรนะ ผมจะถามว่า กินข้าวยัง กินอะไรหรือยัง มันอาจจะเป็นคำง่ายๆ แต่มันแฝงไปด้วยความห่วงใยกัน บางคนเห็นไกลๆได้แต่สบตาแล้ว พยักหน้าให้กัน เหมือนทุกคนในงานเป็นเพื่อน เพื่อนที่พูดจาภาษาเดียวกัน ไม่รู้จะบรรยายออกมายังไงมันรู้สึกดี อิ่มเอมไปหมด ได้แนะนำสินค้า ได้มองเห็นกลุ่มเพื่อนคุยกันสนุกสนาน มันเป็นบรรยากาศที่ดีเลยทีเดียว เอาเป็นว่าเป็นประสบการณ์ที่ดีมากๆ เมื่อเทียบกับปีที่แล้วเลยแหละครับ ขอบคุณ อ.ตั๊ม แม่โบว์ npub1ejn774qahqmgjsfajawy7634unk88y26yktvwuzp9kfgdeejx9mqdm97a5
ที่ให้โอกาสได้ร่วมงาน ขอบคุณเฮียโต้ง สำหรับหนังสือและขนมแสนอร่อยที่เอามาให้เราได้จับจ่ายกัน ขอบคุณ เพื่อนทุกคนที่เข้ามาทักทายกัน ขอบคุณลูกพี่สมนึกหัวหน้าแก๊งค์ร้านเสื้อ พี่แองจี้ แฟนพี่สมนึก แฟนพี่ตั้ม และทีมงานน้องเอิ้น ที่ช่วยขายของ รักทุกคน
siamstr #siamstrog #nostr




-
 @ a10260a2:caa23e3e
2024-10-25 03:41:11
@ a10260a2:caa23e3e
2024-10-25 03:41:11It seems like blogstack is meant to replace Substack if not already apparent by the name. If that's the case, it's already better in a few ways.
1. Hit the ground running
I'm already getting started out of the gate with more readers than I would have if I just started a Substack. This, of course, is due to the fact that I'm creating on top of a protocol where I'm able to have the same audience across all clients of that protocol. This is in stark contrast to the legacy apps from centralized entities where you have to corral your audience from one platform to the next.
2. Readers need not subscribe
Technically, if you're following me, you're subscribed. But you don't have to subscribe for a set price and amount of time (e.g. $5/month or $50/year). I believe this is a win for both of us as I can write my best notes and you can choose to reward me as you see fit. Value 4 value.
3. More conducive to conversation
Writing on Substack felt like writing into a void, with little to no feedback. A post shows up in my readers' inbox and I'll see some stats on whether it was opened or not. That's it. Based on what I've seen so far, blog posts created on Nostr appear in the client apps (e.g Damus, Primal, and Plebstr) as just another note, but with nice formatting and such. From there, I can receive zaps, shakas, comments, and even be reposted.
This is just the beginning. Right now, I'm using blogstack. But what's to stop me from using another tool down the line? I'll have the ability to do so by simply connecting my private key. Can't wait to see what new tools are created in the future.
Bullish on #Nostr
-
 @ a012dc82:6458a70d
2024-10-25 02:23:55
@ a012dc82:6458a70d
2024-10-25 02:23:55Table Of Content
-
Stay Abreast of Market Trends
-
Technical Analysis: Chart the Course
-
Fundamental Analysis: Digging Deeper
-
Follow Expert Insights and Predictions
-
Diversify Your Portfolio
-
Conclusion
-
FAQ
Investing in Bitcoin has become a hot topic in recent years, attracting both seasoned investors and newcomers alike. The potential for significant returns and the excitement surrounding this digital currency make it an attractive choice for those seeking to expand their investment portfolio. However, with great potential comes great risk. The volatile nature of Bitcoin requires investors to stay informed and employ smart strategies to maximize their investments. In this article, we'll explore five proven prediction hacks that can help you navigate the unpredictable world of Bitcoin and enhance your chances of success.
1. Stay Abreast of Market Trends
Keeping up with the latest market trends is essential for any successful investor. In the realm of Bitcoin, this holds even more significance due to its highly volatile nature. By staying informed about market trends, you can identify patterns, understand market sentiment, and make more informed decisions. Regularly monitoring reliable sources of information such as cryptocurrency news websites, influential social media accounts, and industry reports can provide valuable insights that help you stay ahead of the game.
2. Technical Analysis: Chart the Course
Technical analysis is a powerful tool used by seasoned investors to predict price movements based on historical data. By analyzing price charts, identifying patterns, and utilizing indicators, you can gain a deeper understanding of market trends and potential price movements. Whether you're examining candlestick patterns, moving averages, or relative strength index (RSI), technical analysis equips you with valuable information to make well-informed investment decisions.
3. Fundamental Analysis: Digging Deeper
In addition to technical analysis, fundamental analysis helps investors evaluate the intrinsic value of an asset. When it comes to Bitcoin, understanding the underlying technology, adoption rates, regulatory developments, and major partnerships can provide crucial insights into its future prospects. By conducting thorough research and considering these fundamental factors, you can make informed investment decisions based on a comprehensive understanding of Bitcoin's potential.
4. Follow Expert Insights and Predictions
In the world of Bitcoin investments, expert opinions can be invaluable. Keeping an eye on reputable cryptocurrency analysts and influential figures in the industry can provide you with valuable insights and predictions. These experts often share their views through blogs, podcasts, interviews, and social media channels. While it's important to do your own research and not rely solely on others' opinions, expert insights can help you validate your own predictions and make more informed investment choices.
5. Diversify Your Portfolio
Diversification is a key principle in any investment strategy, and Bitcoin is no exception. Spreading your investments across different cryptocurrencies, as well as other asset classes, can help mitigate risks and maximize your chances of profiting. Consider allocating a portion of your investment portfolio to Bitcoin, while also diversifying into other cryptocurrencies or traditional assets like stocks or real estate. By diversifying, you ensure that your financial well-being is not solely reliant on the performance of one asset, reducing potential losses and increasing overall stability.
Conclusion
Investing in Bitcoin can be a thrilling and potentially rewarding endeavor. By employing these five proven prediction hacks, you can navigate the ever-changing landscape of cryptocurrencies with increased confidence and maximize your chances of success. Remember to stay informed, conduct thorough research, and exercise caution when making investment decisions. With the right strategies and a solid understanding of the market, you can unlock the full potential of Bitcoin and optimize your investments.
FAQ
Should I invest in Bitcoin for the long term? While Bitcoin has shown incredible growth over the years, it's important to remember that past performance is not indicative of future results. Investing in Bitcoin for the long term can be rewarding, but it also carries risks. It's crucial to conduct thorough research, consider your financial goals, and seek professional advice before making any investment decisions.
Can I use these prediction hacks for other cryptocurrencies? Absolutely! While this article focuses on Bitcoin, the prediction hacks discussed can be applied to other cryptocurrencies as well. The key is to stay informed, conduct analysis, and consider both technical and fundamental factors when making investment decisions.
Is it possible to predict Bitcoin's price with 100% accuracy? Unfortunately, no prediction method can guarantee 100% accuracy when it comes to Bitcoin's price. The cryptocurrency market is highly volatile and influenced by various factors, making it challenging to predict with absolute certainty.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 502ab02a:a2860397
2024-09-17 03:02:24
@ 502ab02a:a2860397
2024-09-17 03:02:24เหนื่อยกาย อาบน้ำก็หาย ความประทับใจ มันจะประทับไปอีกนาน
น้ำนี่มีประโยชน์กับมนุษย์สูงมาก โดยเฉพาะน้ำใจ
Thailand Bitcoin Conference 2024 ที่ผ่านมา 2 วัน 14-15 september 2024 block 861367 เป็นงานที่ตอนนี้ผมนั่งตกตะกอน บันทึกไว้ใน long form ของ YakiHonne ที่ต้องขอบคุณมากๆ เพราะคุณ Wendy มาที่บูธผม หลังจากแนะนำตัว ผมบอกว่าใช้ YakiHonne อยู่ คุณ Wendy ถามว่า user ชื่ออะไร พอเปิดแอพถึงแค่หน้า feed ที่มีรูปผมกลมๆเล็กมุมขวาบน ยังไม่ทันกดเมนู profile เพื่อแสดงชื่อ คุณ Wendy ก็ชี้รูปแล้วบอก i know you ทันที ซึ่งน่าตกใจและประทับใจมากๆ

ใน YakiHonne ผมมีหัวข้อ ”เจอนี่“ ที่เอาไว้บันทึกเรื่อง เจอนี่ อยู่แล้ว การที่ได้เจอ ชาวบอทคอยน์,ทุ่งม่วง และ Wendy จึงเหมาะกับคอลัมน์ เจอนี่ที่สุดแล้ว
หลังจากแผน Mission unknown ลุล่วงไปได้ มี error ไว้ให้แก้บ้างซึ่งวางแผนสองไว้แล้ว แต่ก็เหนือความคาดหมาย จาก Mission unknown กลายเป็น Mission Impossible ไปด้วยการทำ world records ของตัวเอง 2 วันซ้อนคือ 64ก้อน ภายใน 2 ชั่วโมงในวันแรก และ 80ก้อน ภายใน 50นาที (8:30-9:20) วันที่สอง
เรื่องเค้ก เดี๋ยวไปสวมหมวกกุ๊กเขียนในตำรับเอ๋บนสื่อมาร์กนะครับ ในนี้ผมอยากบันทึกเรื่องคอมมูทุ่งม่วงมากกว่า
ต้องขออภัยที่ไม่ได้แทกหรือระบุชื่อใคร เหมือนตอนซื้อสติกเกอร์อะครับ ผมรักพวกคุณเท่าๆกันหมดเลย กลัวว่าเอ่ยชื่อไม่หมดผมเองจะเสียใจ
ครั้งนี้เป็นครั้งแรกที่ผมได้เจอชาวทุ่งม่วง ขอบคุณที่แนะนำตัวกันด้วยชื่อในทุ่งม่วง ไม่งั้นนี่ผมต้องไปไม่เป็นแน่ๆครับ โชคดีที่ชาวทุ่งม่วงมารวมกระจุกตัวที่ตลาดสายฟ้า ขอบคุณ มิก ที่เป็นแม่เหล็กดูดคนไว้ไม่ให้ไปไหน จนฝั่งทุ่งม่วงคาเฟ่ของเรา กลายเป็นจุดรวมพลคนทุ่งม่วงไปเลย
ตามที่ตั้งใจไว้ครับ ว่าชีวิตผมหลังจาก 31 กรกฎาคม 2567 จะเป็น chapter ใหม่ ของการใช้ชีวิต ผมจะพยายามหลอมรวมทรัพยากรที่มีค่าที่สุดในโลกที่เรียกว่า “เวลา” มาใช้จ่ายให้คุ้มที่สุด หลังจากที่เลือกหันหลังให้อาชีพที่หลายๆคนมองว่ามั่นคง แต่มันดูดเวลาผมไปแทบจะหมดตัว จนตัวเองมองว่า ทรัพย์ในมือเราแท้ๆ จริงๆแล้วเวลามันอยู่ในกระเป๋าเรา ตัวเราเองไม่ใช่เหรอที่หยิบมาจ่ายออกไป เราเลือกจะจ่ายให้กับอะไรไม่รู้ แทนที่จะจ่ายให้คนที่เรารัก นี่มันสุรุ่ยสุร่ายนี่หว่า
ดังนั้น
ผมกลับมาใช้บั้นปลายชีวิต ด้วยการจ่ายที่มีคุณค่าขึ้น ผมเรียกการใช้จ่ายนี้ว่า spend time ยิ่งเหลือน้อยยิ่งต้องใช้แบบมีคุณค่า ผมไม่ได้ออมเวลามาตั้งแต่วัยรุ่น ผมเลยไม่มั่งคั่งในเวลา นี่จะ 50 อยู่รอมร่อ ถ้าคำว่า make saving great again ไม่ผ่านหูผ่านตามา ผมคงไม่ save time เพื่อเอาไป spend time ที่มีคุณค่าได้ครับ เรียกว่า กลับตัวยังทันในวันที่มีลมหายใจ จึงเลือกที่จะ ประหยัดเวลาเพื่อเอาไปใช้จ่ายกับสิ่งที่มีคุณค่า
ความอบอุ่นที่ได้รับจากคอมมูนิตี้ มันมีพลังมากๆเลยครับ ไม่ผิดกับที่คาดไว้หลังจากได้อ่านมาจากหลายๆอีเวนท์ที่เกิดขึ้น
เหมือนที่ยืนคุยกับหมอเอก กับ คุณริช ครับว่าภาพความสำเร็จของงานมันแสดงออกมาทางหน้างานนี่ละครับ ความครึกครื้น การพูดคุยกัน sats สะพัด มันเหมือนเราเห็นภาพอนาคตได้ในวันนี้ บรรยากาศแห่งน้ำใจ บรรยากาศการใช้บิทคอยน์แลกสินค้าที่มาจากความตั้งใจในการทำ ผมมั่นใจเลยว่า สินค้าตลาด lighting ล้วนเกิดจากอิทธิบาท4 แม้แต่ฝั่งเบียร์ มันมาจาก passion ทั้งนั้นเลย ภาษาบิทคอยน์อาจเรียกว่าตลาดนี้เป็นศูนย์รวมของ proof of work
นึกถึงตอนวัยรุ่น เวลาคนมีไฟมารวมกัน มันคือพลังระดับ ดวงอาทิตย์
ถ้ามันเป็นแบบนี้ตลอดไป ก็ไม่มีอะไรที่ภายในทุ่งม่วงนี้ ที่ทำไม่ได้แล้วหละครับ

ยินดีและปรีดา ที่ได้พบทุกท่านจริงๆครับ ทุกท่านกลายเป็นตัวหนังสือที่ออกมาโลดแล่นบนโลกจริงๆ ภาพในหัวตอนนี้เวลาเห็นตัวหนังสือก็จะฝังหน้าลงไป embed เรียบร้อย เหมือนแต่ละ block ที่ฝังเหตุการณ์เอาไว้
ท้ายสุด ด้วยความนิยมชมชอบในงานของกันและกัน พ่อมดคริปโต ได้มอบการ์ด prototype จากบอร์ดเกมส์ Age of Bitcoin Boardgame ให้ผมเป็นที่ระลึก ก่อนรับรางวัลที่ 1 กิจกรรม geyser ทำให้เป็น rare item ในทันที ขอบคุณ ชับบี้ มากๆครับ

ขอบคุณพี่ป้ำ เป็นพิเศษสำหรับ DM ตอนก่อนเตรียมงานและการสนทนาภาษา baker ในงานครับ
ถึงทีม Right Shift ทุกคนครับ "ผมเป็นอีกคนที่มีความสุขนะครับ" ผมในฐานะที่อยู่วงการโฆษณา ประเภท below the line และ ออกาไนเซอร์ มาก่อน ยืนดูงานแล้ว ต้องขอขอบคุณที่เหนื่อยกันนะครับ break the leg จริงๆ
ปล. ด้วยว่าส่วนตัวความจำระยะสั้นผมแย่มาก ผมมักจำด้วยภาพ ใครที่ผมได้มองหน้าบ่อยผมจะ match ชื่อไปกับหน้าด้วยเลย แต่งานนี้ information overload ทั้งขายของ ทั้งทักทาย ประกอบกับนอนน้อยมากด้วย ผมจำใครไม่ได้บ้างก็โปรดให้อภัยครับ คิดเลขยังเครื่องคิดเลขเลย
ถ้าได้เจอตามท้องถนน เรียกทักกันด้วยนะครับ ผมยินดีและอยากคุยครับ ส่วนถ้าผมเดินผ่านคุณไปทักเลยนะครับ เพราะนอกจากความจำสั้นแล้วสายตายังยาวด้วยครับ
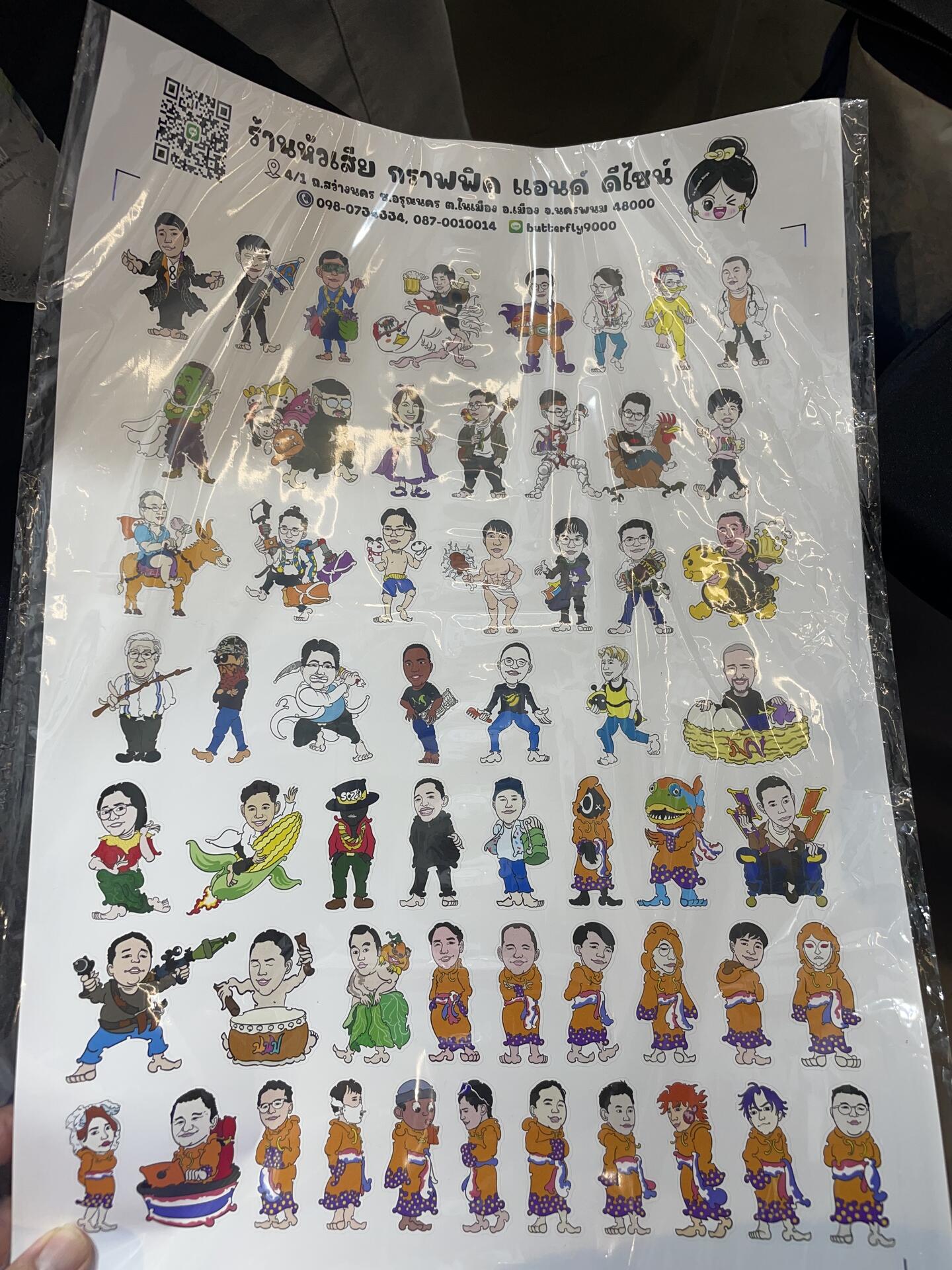
-
 @ 862fda7e:02a8268b
2024-09-16 22:59:38
@ 862fda7e:02a8268b
2024-09-16 22:59:38I was in some sort of nice romantic building and I met this nicer middle aged blonde woman who looked a lot like one of my old teachers. We got to chatting and things started moving quickly, we were going to have sexy lesbian sex but she told me she wanted me to shave my vagina before we started. I said fine, went to a bathroom and started shaving. If it meant I was going to slang some tang, I was gonna do it. It took me a long time to complete this daunting task, as I've mantioned many times before, I have a very thick and dense bush. I also wanted to make sure no hair was left behind, if my sweet lesbian lover saw that I had a hair on my vagina, she would probably freak out and call me disgusting for having a feature that naturally grows on me.
Anyways, I finished shaving my vagina and went to go meet her. Sadly, she decided to not have lesbian sex with me anymore since I took too long and she had some time to think about it. I got screwed without getting screwed. And now I had a gross hairless vagina.
I think I know why this dream occured. It's because my so called "fans" have judged me on my fan page for having hair on my vagina. Yes, I sometimes maintain it and keep it trimmed, sometimes. But sometimes I just let it go if I'm too lazy. Now the lesbians in my dreams want me to shave, and even at that, they still don't want to have sex with me. One time I remember cumming from a wet dream I had, which is very rare for me to do. I was watching 2 Japanese chicks dressed up in the school girl uniform scissor, and I remember waking up with a hard clit and it pulsated. I felt embarassed waking up, because I didn't even voluntarily masturbate but I still climaxed.
-
 @ a10260a2:caa23e3e
2024-10-25 01:51:45
@ a10260a2:caa23e3e
2024-10-25 01:51:45A zero-dependency, zero-framework QR code web component for Bitcoin on-chain, Lightning, and unified BIP-21 payments.
Just discovered this tool by nostr:npub18agram6s6kulwwhc638d8q8y5vysutrrvvdll2wdjxd75wp4dfjqshytrf and found it to be very useful. Also, did I mention easy-to-use?
You can find the GitHub here and a demo I made (complete with a function to check for payment) on the Bullish Prototype. 👨💻
originally posted at https://stacker.news/items/737255
-
 @ 7fa56f5d:751ac194
2024-09-16 12:31:25
@ 7fa56f5d:751ac194
2024-09-16 12:31:25If you are a nostr user or developer you're probably familiar with nostr identifiers. These identifiers are used to represent public/private keys or event ids. They allow for a human-readable representation of these values that can be used for copy-pasting, sharing, nostr URIs, rendering QR codes or referencing entities in text content.
The identifier start with a prefix that indicates the type of the identifier:
npubfor public keys,nsecfor private keys andnotefor note ids. The prefix is followed by a separator character (1) and a payload that is encoded using the Bech32 encoding scheme.The pubkey
7fa56f5d6962ab1e3cd424e758c3002b8665f7b0d8dcee9fe9e288d7751ac194is represented asnpub107jk7htfv243u0x5ynn43scq9wrxtaasmrwwa8lfu2ydwag6cx2quqncxg.Context matters
There are special variants of the identifiers that include metadata to provide more context. The extra information enhances nostr client UX and interoperability since it allows to more easily find and display these entities.
The
nprofileprefix is used to represent a public key with a set of relays where the user profile can be found. Theneventprefix is used to represent an event id (not necesarily a kind 1 note) with an optional set of relays where the event has been seen, the author of the event and an optional kind number. Thenaddrprefix is used to represent an address with kind, author, identifier (d) and an optional set of relays where the event has been seen.For those variants the content is a binary-encoded list of
TLVfields. Check out NIP-19 for a breakdown of which types are used for each prefix.Pubkeys
Although there are relays that aggregate profile metadata and relay lists such as Purple Pages and profiles.nos.social, a bare
npubis not enough to find a user's content. Thenprofilealternative prefix tells clients where they can find the user's profile and posts.Some great options for the relay hints included in an
nprofileare the relays on the user's relay list metadata event.Events
An
neventidentifier can contain additional metadata about the event such as relay hints, the author of the event and the kind number. The relay hints can be used to find the event on the network and the author can be used to display the author's profile picture and name.Including the kind number in the identifier is useful for clients since they can know if the event is compatible with their rendering logic. A client that only supports kind 1 notes can ignore kind 9802 highlights or show their
.contentfield. A better alternative would be to query the nostr network to find compatbile apps via NIP-89 Recommended Application Handlers or even embed the apps in the client itself.Addresses
There are certain types of events that do not have stable identifiers since they can be replaced anytime. A user can publish new versions of long-form articles or their profile. The
naddrprefix is used to represent these events with an identifier that can be used to find the latest event. Thedfield is used to represent the identifier of the event that the address points to.Similary to
nevent, thenaddrprefix can include relay hints to find the event on the network. The author field can be used to display the author's profile picture and name. The kind field can be used to know if the event is compatible with the client's rendering logic.tl;dr
I encourage developers to use the variants with added context whenever possible. This means that clients will need to keep track of which relays an event has been seen on and which relays a user is posting to and reading from. The trade-off between longer identifiers and better interoperability is worth it if we want to make the nostr network decentralized and resilient.
You can use tools such as nak to get familiar with the different types of identifiers, add or remove metadata to your identifiers and decode them.
-
 @ dd32f3e0:498f1df9
2024-10-25 01:42:06
@ dd32f3e0:498f1df9
2024-10-25 01:42:06eyJfaWQiOiJkMmVkZDBkMy0yZmM3LTQxNWYtYTA5MC1iY2Q2ZDE2YTc2YjYiLCJwdWJsaWNLZXkiOiJkZDMyZjNlMDgzNDdlYTYzM2U2MzZkODlhMjMzOWQ0N2IyOTM2MWZkZTQ3MTZjZjNhZTBhMzhhYTQ5OGYxZGY5IiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6IkZJWEVEIiwibWFyZ2luIjowLCJtYXJrZXRQcmljZSI6bnVsbCwiZml4ZWRQcmljZSI6MTUwLCJtaW5BbW91bnQiOjAsIm1heEFtb3VudCI6NTAwLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoibmljZSB0cmFkZXIiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yNVQwMTo0MjowNi4yNzBaIn0=
-
 @ 6f0ba1ef:58eb4351
2024-10-25 01:16:41
@ 6f0ba1ef:58eb4351
2024-10-25 01:16:41eyJfaWQiOiIzMjFkMjkyNi0xOGUyLTRjYTgtOWIwYy0xNGMwNWExZDc4ZTAiLCJwdWJsaWNLZXkiOiI2ZjBiYTFlZjc4YjE3ZTVkMjNkMmVjZDlkYWNlNmJhMzBlODI1NzUxMGY0NmYxNjA0NGUyZjY5ZjU4ZWI0MzUxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MywibWFya2V0UHJpY2UiOjE1Ny40NiwiZml4ZWRQcmljZSI6MCwibWluQW1vdW50IjoxMCwibWF4QW1vdW50IjoyMDAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsInBheW1lbnRNZXRob2REZXRhaWwiOiJ2ZXJ5IGZhc3QgYW5kIGVhc3kiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yNVQwMToxNjo0MS41MDBaIn0=
-
 @ 502ab02a:a2860397
2024-09-14 08:26:05
@ 502ab02a:a2860397
2024-09-14 08:26:05
YakiHonne คือแพลทฟอร์ม long form ที่ผมมักใช้ประจำในการทำบทความยาวๆ มาวันนี้ได้เจอคุณเวนดี้ ที่งาน Thailand Bitcoin conference 2024 รู้สึกดีใจมากๆ
siamstr
-
 @ 4ba8e86d:89d32de4
2024-10-24 23:42:27
@ 4ba8e86d:89d32de4
2024-10-24 23:42:27Um canal Lightning pode ser pensado como uma sequência de contas esticadas entre duas pessoas. Consultando a Fig. 1, Alice pode pagar Bob empurrando uma de suas contas para o lado dele. Se Bob também tiver um canal Lightning com Carol, Alice pode pagar Carol por meio de Bob: ela empurra uma conta para Bob, que então empurra uma conta para Carol. A regra fundamental — e a razão por trás dos problemas de liquidez da Lightning Network — é que as contas podem se mover de um lado para o outro, mas não podem sair do cordão em que estão.
https://nostrcheck.me/media/public/nostrcheck.me_7999139148267863241703513103.webp Fig. 1. Alice pode enviar um pagamento para Carol roteando-o por Bob. Como as contas não podem sair do cordão em que estão, Bob acaba com uma conta a mais em seu cordão com Alice e uma conta a menos em seu cordão com Carol.
Isso é tudo que você precisa saber para entender como o dinheiro pode fluir na Lightning Network. No entanto, esse modelo não nos diz nada sobre por que os pagamentos na Lightning são seguros. Por exemplo, o que impede Bob de simplesmente manter a conta que Alice empurrou para ele e nunca enviar uma para Carol? O objetivo deste artigo é responder à pergunta "o que torna os pagamentos na Lightning 'sem confiança'?"
Ao final do artigo, revelaremos o sujo segredinho da Lightning Network: que os pagamentos pequenos não são realmente "sem confiança" — nós nós de roteamento podem perder fundos dos clientes.
Contratos Hash-Time-Lock (HTLCs) Para explicar o que impede Bob de manter a conta de Alice sem enviá-la para Carol, precisamos introduzir "travas" em nossa analogia física para os canais Lightning. Travas podem ser colocadas nos cordões para restringir o movimento das contas e só são abertas se condições específicas forem atendidas. Os contratos hash-time-lock (HTLCs) usados nos pagamentos Lightning envolvem dois tipos de travas (cf. Fig. 2): a primeira é uma trava que se abre se apresentada com a senha correta (vamos chamá-la de "hash-lock"), e a segunda é uma trava que se abre automaticamente após um atraso de tempo (vamos chamá-la de "time-lock").
https://nostrcheck.me/media/public/nostrcheck.me_9607840347208938921703514339.webp Fig. 2. O hash-lock se abre quando uma senha é inserida e gera o valor especificado (45f8 neste caso). O time-lock se abre após o tempo especificado ter decorrido (48 horas neste caso).
Agora, voltemos ao pagamento de uma conta de Alice para Carol por meio de Bob. Para tornar o pagamento "sem confiança", Alice, Bob e Carol precisam estar online ao mesmo tempo e participar de um elaborado ritual.
Primeiro, Alice pede a Carol que pense em uma senha secreta e diga a ela o hash da senha. Vamos fingir que a senha que Carol inventou foi "boondoggle" e seu hash foi "45f8". Em seguida, Alice coloca um hash-lock entre ela e Bob, configurado para abrir quando apresentado com uma senha que gera o hash "45f8". Neste ponto, nem Alice nem Bob podem abrir a trava, pois nenhum deles conhece a senha. Alice então empurra uma conta contra o hash-lock. Por fim, ela coloca um time-lock no lado esquerdo da conta, configurado para abrir automaticamente após 48 horas (Fig. 3).
https://nostrcheck.me/media/public/nostrcheck.me_3127046972622599461703514704.webp Fig. 3. Com o conhecimento do hash da senha secreta de Carol, Alice pode configurar um hash-lock para proteger a conta que ela transfere para Bob (para depois encaminhar para Carol). Ela trava a conta com um time-lock para que ela possa recuperá-la caso Bob não conclua o pagamento dentro de 48 horas.
Bob percebe que a conta é dele se conseguir descobrir a senha antes de 48 horas se passarem. Ele também sabe (porque Alice disse a ele) que Carol revelará a senha em troca de uma de suas contas. Para incentivar Carol a agir, Bob coloca o mesmo hash-lock entre ele e Carol, empurra uma de suas contas e então a trava com outro time-lock (Fig. 4). Ele sabe que, para Carol abrir o hash-lock e pegar a conta, ela precisará inserir a senha — à vista de todos — que é a mesma senha que Bob precisa para abrir o hash-lock com Alice.
https://nostrcheck.me/media/public/nostrcheck.me_4635793414256087711703515032.webp Fig. 4. Bob percebe que a conta de Alice é dele se Carol revelar sua senha antes de 48 horas. Ele configura o mesmo hash-lock, empurra uma conta em direção a Carol e a trava com um time-lock. A única maneira de Carol pegar a conta de Bob é revelar a senha que Bob precisa para reivindicar a conta de Alice.
Carol, ao ver que a conta está lá para ser pega, insere "boondoggle" na trava (lembre-se de que está à vista de Bob). A CPU da trava confirma que hash("boondoggle") = 45f8, e então se abre. Carol move a conta para o lado dela do cordão (Fig. 5).
https://nostrcheck.me/media/public/nostrcheck.me_6790828350788856531703516541.webp Fig. 5. Carol revela sua senha para abrir a trava e pegar a conta.
Com o conhecimento da senha de Carol, Bob desbloqueia sua conta de Alice da mesma forma (Fig. 6). O pagamento está completo.
https://nostrcheck.me/media/public/nostrcheck.me_8432131267156524571703517282.webp Fig. 6. Com o conhecimento da senha secreta de Carol, Bob pode agora pegar a conta de Alice, completando assim o pagamento.
Você pode se perguntar por que Bob se incomodaria em participar desse ritual em primeiro lugar. Se Carol não tivesse sido cooperativa, sua conta poderia ter sido congelada até que o time-lock expirasse. Na prática, Alice enviaria a Bob um pouco mais do que ela pede a Bob para enviar a Carol, como uma taxa para compensar por esse risco e pelo esforço de Bob. Quando o pagamento estiver completo, Bob terá um pouco mais do que começou, motivando-o assim a concluir o pagamento.
Você também pode se perguntar qual é o propósito dos time-locks. Os time-locks permitem que os participantes recuperem seus fundos se o pagamento falhar. Por exemplo, imagine que Bob se torna não cooperativo depois que Alice transfere sua conta e adiciona os dois locks. O time-lock é o que permite a Alice recuperar seus fundos. Ela só precisa esperar o time-lock expirar. Não há como Bob roubar a conta nesse ínterim, porque ele precisa da senha de Carol, o que ele não pode obter sem dar a Carol uma de suas contas e, assim, completar o pagamento.
Leitores interessados podem explorar o que acontece se uma das partes se tornar não cooperativa em diferentes etapas do processo de pagamento do Lightning para se convencer de que nem Alice, Bob, nem Carol estão em risco de perder dinheiro devido às ações de suas contrapartes.
O Sujo Pequeno Segredo da Lightning Network A Lightning Network tem um sujo pequeno segredo que poucas pessoas conhecem. Para entender qual é o segredo — e suas ramificações para os pagamentos do Lightning — precisamos cavar um pouco mais.
Lembre-se de que quando Alice enviou o pagamento para Carol através de Bob, o estado intermediário mostrado na Fig. 7 existia. Quando expresso como uma transação de bitcoin, o estado do canal contém três saídas: as moedas de Alice, as moedas de Bob e a moeda "em voo".
https://nostrcheck.me/media/public/nostrcheck.me_9561697518547468611703528026.webp Fig. 7. A transação de estado do canal Lightning neste ponto do tempo contém três saídas: as moedas de Alice, as moedas de Bob e as moedas em trânsito.
Aqui está o problema: se o valor em trânsito estiver abaixo do limite de poeira do BTC, então não pode ser representado como uma terceira saída na transação de estado do canal! Portanto, não é possível usar hash- e time-locks para proteger o pagamento se o pagamento for muito pequeno.
Para explicar como o LN lida com esse problema, devo primeiro fazer uma confissão. Não é exatamente verdade que o número de contas em uma string seja constante. Na verdade, há um balde ao lado de cada string rotulado como "Taxa do Minerador" que contém pequenas frações de contas. O valor neste balde é reivindicado pelo minerador que confirma a transação de estado do canal, caso o estado do canal seja empurrado para o blockchain. Frações de contas podem se mover da string para o balde, ou do balde de volta para a string, mas apenas se as pessoas em ambos os lados do canal concordarem.
Em vez de travar o valor em trânsito com hash- e time-locks, para pagamentos pequenos, Alice e Bob simplesmente movem o valor em trânsito para o balde de taxas (Fig. 8). Bob confia que Alice cooperará com ele para retirar o valor em trânsito do balde de taxas quando ele revelar a senha secreta de Carol.
https://nostrcheck.me/media/public/nostrcheck.me_3836418249379116631703528340.webp Fig. 8. Se as moedas em trânsito estiverem abaixo do limite de poeira, o mecanismo HTLC não pode ser usado porque a transação de estado do canal não seria minerada se fosse transmitida. Em vez de usar o mecanismo HTLC, as moedas em trânsito são despejadas no balde de "Taxa do Minerador".
https://nostrcheck.me/media/public/nostrcheck.me_3836418249379116631703528340.webp Fig. 8. Se as moedas em trânsito estiverem abaixo do limite mínimo ("dust threshold"), o mecanismo HTLC não pode ser usado, pois a transação do estado do canal não seria minerada se transmitida. Em vez de utilizar o mecanismo HTLC, as moedas em trânsito são depositadas no "Miner's Fee" (Taxa do Minerador).
Neste esquema alternativo, Bob transfere o valor em trânsito para um segundo compartimento de taxas que ele compartilha com Carol, prometendo entregá-lo a ela se contar a Bob a senha secreta. Carol revela o segredo a Bob, e juntos movem o pagamento do compartimento de taxas para o lado de Carol. Bob então volta para Alice, conta a ela o segredo de Carol e, se tudo correr bem, Alice coopera com ele para retirar o valor em trânsito do compartimento de taxas e colocá-lo no lado de Bob da sequência.
Ao contrário do esquema HTLC descrito anteriormente, este esquema depende da confiança. Por exemplo, Carol poderia revelar a senha a Bob, que poderia deixar o pagamento no compartimento de taxas e ainda assim ir a Alice e entregar a senha em troca de seu pagamento.
As opções de Carol nesse cenário são limitadas: ou ela não faz nada e aceita a perda, ou ela encerra o canal com Bob. No entanto, encerrar o canal com Bob não a deixa totalmente compensada, pois o valor que ela deveria ter recebido é enviado para um minerador!
Apesar de parecer quebrado, esse esquema realmente funciona razoavelmente bem na prática. Bob não tem um incentivo real para não dar o dinheiro a Carol. Se ele não devolver, ele não ficará em uma situação melhor (o minerador ficará com os fundos extras, não ele) e provavelmente em uma situação pior (Carol provavelmente fechará o canal, já que Bob se mostrou não confiável). O dano que Bob pode causar parece limitado ao valor do pagamento mais o custo de estabelecer um novo canal relâmpago.
Por que isso é significativo O segredo sujo do Lightning é significativo porque revela como a fricção da Camada 1 (L1) vaza para a L2, forçando soluções complexas e mal compreendidas¹ para o protocolo L2. A solução alternativa neste caso alterou a natureza "sem confiança" dos pagamentos do Lightning: para pagamentos acima do limite de poeira, nem Alice, Bob, nem Carol podem perder dinheiro devido às ações de suas contrapartes. Para pagamentos abaixo do limite de poeira, Alice, Bob e Carol podem perder dinheiro sem culpa própria. É um modelo de segurança fundamentalmente diferente do que as pessoas entendiam.
Alguém poderia argumentar: "estamos falando apenas de pagamentos pequenos, então quem se importa?" Eu não concordo com esse argumento por duas razões:
-
O plano de escalonamento do Core, usando o blockchain como uma camada de liquidação com taxas elevadas, aumentará o limite para o que constitui "poeira". Poeira são saídas que não podem ser gastas economicamente porque a taxa on-chain para gastá-las é maior do que seu valor. Com taxas de $100, a maior parte do salário mensal de todo o mundo é "poeira".
-
Perder vários pagamentos pequenos em rápida sucessão (por exemplo, devido a um ataque de roteamento no LN) poderia resultar em uma perda significativa.
Imagine um futuro em que a maioria dos pagamentos ocorra na Lightning Network, e as taxas de transação na L1 sejam consistentemente superiores a $100. As saídas de poeira abaixo de $100 na mainchain não têm valor porque custa mais gastá-las do que valem.
Agora a Lightning Network enfrenta o problema de que até mesmo pagamentos de $50 não são "sem confiança". No caso em que $50 estão abaixo do limite de poeira (o que seria uma política razoável considerando que $50 seria economicamente impossível de gastar na L1), então os HTLCs não podem ser usados para proteger o pagamento de $50. Os clientes podem perder pagamentos de $50 sem culpa própria.
No caso em que os desenvolvedores tentam contornar alguma "brecha legal" definindo o limite de poeira como $1 para que os HTLCs ainda possam ser usados, o efeito ainda é uma perda de $50 para o cliente, pois a saída não será economicamente gasta! Os clientes ainda podem perder pagamentos de $50 sem culpa própria.
Alguém poderia argumentar "bem, os nós de roteamento podem perder fundos dos clientes e esses fundos podem ser significativos em um futuro com taxas altas, mas os nós de roteamento são pares, não empresas." Eu também não concordo com isso porque o objetivo principal do roteamento de pagamentos do Lightning é ganhar dinheiro em taxas de transação em troca de empréstimo de liquidez. Já hoje, os desenvolvedores do Lightning abandonaram a ideia de que todos os usuários roteariam pagamentos; agora é incentivado que usuários normais usem canais não divulgados e nunca roteiem.
Em um futuro com altas taxas, um hub tem controle custodial efetivo sobre o dinheiro de seus usuários. Um usuário não pode liquidar no blockchain para recuperar fundos de pagamentos não protegidos por HTLCs. Além disso, se o saldo do usuário estiver na mesma ordem de grandeza das taxas on-chain, o usuário também está preso ao hub. Não vale a pena escapar de um canal "ruim", pois isso custaria ao usuário todo o seu saldo. Hubs também podem bloquear os fundos do cliente indefinidamente, recusando-se a rotear pagamentos a menos que certas condições sejam atendidas (por exemplo, desembrulhar as informações de roteamento de cebola para fins de AML/KYC). A única escolha do usuário é liquidar no blockchain e perder todo o seu dinheiro — o que não é uma escolha real! Hubs também podem roubar seus usuários na forma de taxas exorbitantes. Novamente, o usuário está preso e não tem escolha a não ser pagar se quiser acessar seu dinheiro.
Hubs significativamente conectados na Lightning Network, em um futuro com taxas elevadas na camada base, deveriam ser regulamentados devido ao controle efetivo que possuem sobre os fundos de seus clientes.
Gostaria de propor a hipótese de que o seguinte princípio existe:
Pagamentos na Camada 2, para quantias abaixo do que é economicamente viável na Camada 1, não podem alcançar uma natureza "sem confiança".
A eficácia do Lightning depende da liberdade da blockchain subjacente, alinhando-se com as expectativas dos usuários.
Isso é apenas uma das muitas razões pelas quais um futuro em que a maioria das transações ocorre na Lightning Network e a blockchain possui taxas elevadas será muito diferente do que as pessoas esperam. Outras razões incluem:
-
O Lightning dimensiona transações, não usuários. O custo de operar um nó completo de validação ainda será alto.
-
A fricção na Camada 1 afeta a fungibilidade na Camada 2; as moedas têm um valor dependente da posição.
-
Liquidez: a maioria dos "estados de riqueza" não é alcançável por meio de transações na Lightning. Falhas em pagamentos são inevitáveis.
-
Roteamento é difícil se o grafo de rede for extenso: os hubs da Lightning tenderão a se centralizar para reduzir problemas de roteamento e liquidez.
-
A experiência típica do usuário ao executar uma carteira não custodial sempre será complicada: os usuários precisam estar online para receber dinheiro, contratar torres de vigilância para monitorar fraudes em canais, assinar serviços de roteamento de origem para enviar pagamentos e fazer backup dinâmico de seus estados de canal contra corrupção de dados.
-
Risco sistêmico: uma quantidade muito grande de moedas precisa ser bloqueada em canais da Lightning (carteiras quentes) para fornecer a liquidez necessária.
-
As taxas agregadas dos mineradores na Camada 1 não serão suficientes para garantir a segurança da blockchain quando a recompensa por bloco se esgotar.
Esse texto apontar que LN não é “sem confiança” para pequenos pagamentos e que os fundos dos clientes poderiam ser redirecionados para o mineradores sem culpa do cliente. A crença amplamente difundida, mas falsa, dentro da comunidade BTC era que todos os pagamentos Lightning eram “sem confiança” por design .
-
-
 @ 79008e78:dfac9395
2024-09-12 11:16:45
@ 79008e78:dfac9395
2024-09-12 11:16:45" ผมตื่นเต้นที่จะประกาศเปิดตัว NWS ครั้งแรก นี่เป็นคำตอบของการเชื่อมต่อออกไปยังโลกของอินเตอร์เน็ต โดยใช้ NOSTR เข้าไปแทรกระหว่าง transport layer และ network layer ที่อยู่บน TCP/IP โมเดล NWS นั้นจะเข้ามาช่วยให้การสื่อสารระหว่างอุปกรณ์ต่างๆ ให้เป็นไปอย่างราบรื่น มีความเป็นส่วนตัวเพิ่มขึ้น และทำให้เราสามารถท่องโลกของอินเตอร์เน็ตโดยไม่จำเป็นต้องใช้ Public IP " -asmogo
NostrWebServices (NWS) คืออะไร?
NWS คือการนำ Nostr เข้ามาช่วยในการเข้าถึงบริการของเว็บไซต์ต่าง ๆ โดยยังสามารถส่งข้อมูลขึ้นไปยัง transport layer บน TCP/IP ซึ่งด้วยวิธีนี้เองเลยทำให้เราสามารถสร้างการเชื่อมต่อได้โดยไม่จำเป็นต้องมี Public IP โดยส่วนที่จำเป็นหลัก ๆ ในการทำงานนี้เราจำเป็นต้องเตรียม
-
Entry node: SOCKS5 proxy ที่คอยส่งต่อ TCP packets ที่เข้ารหัสผ่านทาง event ของ Nostr ก่อนส่งส่งผ่านรีเลย์ต่าง ๆ ไปยัง Exit node
-
Exit node: TCP reverse proxy ที่คอยรอรับข้อมูลมาจาก Entry node และส่งต่อข้อมูลต่าง ๆ ไปยังบริการอื่น ๆ ต่อไป

ในส่วนของการทำงานนั้นสามารถดูได้จากในรูปที่ได้แนบไว้ข้างต้นได้เลย อย่างที่เห็นเลยว่ามันเริ่มจากแอพต่าง ๆ เหมือนที่เรามีการใช้งานกันอยู่ในปัจจุบัน เพียงแต่แทนที่เราจะส่งข้อมูลต่าง ๆ ผ่าน IP layer ตามปกติ เราสามารถส่งเข้าไปยัง Entry node และหลังจากนั้นข้อมูลจะถูกส่งผ่าน relay ต่าง ๆ ก่อนที่จะวิ่งไปยัง Exit node และ Exit node จะคอยส่งข้อมูลต่าง ๆ ไปยังบริการหลังบ้านที่เราต้องการจะเชื่อมต่อ
เราจะเห็นได้ว่าการทำงานของ NWS นั้น สำหรับผู้ใช้งานโดยทั่วไปแล้วแทบจะไม่แตกต่างอะไรกับในปัจจุบันเลย นั่นก็เพราะว่าเรายังทำการใช้งานแอพต่าง ๆ ตามปกติ แต่ประโยชน์ที่เราจะได้รับเพิ่มเติมนั้นคือความเป็นส่วนตัวในการใช้บริการเบื้องหลังอื่น ๆ
นอกจากนี้ยังมีในส่วนของ NWS domain names ใน NWS นั้นมีการรับรอง domain สองตัวนั้นคือ
- ".nostr" ซึ่งใช้ชื่อโฮสต์เป็นกุญแจสาธารณะที่เข้ารหัสด้วย base32 และ รีเลย์ที่เข้ารหัสด้วย base32 เป็นโดเมนย่อย
- "nprofiles" ซึ่งเป็นการผสมผสานกันระหว่างกุญแจสาธารณะของNostrและรีเลย์หลายตัว
ซึ่งโดเมนทั้งสองประเภทจะถูกสร้างและปรากฏอยู่บนคอนโซลเมื่อเริ่มต้นใช้งาน
หัวใจหลักในการทำงานของ NWS
อย่างที่ได้กล่าวไว้ข้างต้นว่า NWS เข้ามาช่วยเหลือในการเพิ่มความเป็นส่วนตัวได้ แล้วถ้าเราไม่ได้ต้องการเข้ารหัส หรือถ้าเราอยากจะเปิด Entry node แล้วเราไม่ต้องการให้คนที่จะเชื่อมต่อเข้ามาเข้ารหัสข้อมูลเราสามารถทำได้เช่นกัน โดยทั้งสองระบบที่ NWS ทำได้มีดังนี้
-
แบบไม่เข้ารหัส: เราจำเป็นต้องรันโหนดไว้ในเครื่องที่เราใช้รัน client แล้วแปลง client ให้ส่งข้อความใส่โหนดปลายทางตรง ๆ
-
แบบเข้ารหัส เริ่มจากการเชื่อมไปที่โหนดที่ต้องการ (อารมณ์ ssh เข้าไป) แต่วิธีนี้ยังติดที่บางเว็บที่เป็น https จะเชื่อมไม่ได้หาก cert ของโหนดที่เราเชื่อมมีปัญหา ส่วนข้อมูลที่ส่งจะถูก encrypt ไว้ด้วย Sphinx (เข้ารหัสแบบหนึ่งในมาตรฐาน RSA) ฉนั้นมั่นใจได้ว่าโหนดที่เราไปยืมจมูกเขาหายใจก็ไม่รู้ว่าเราส่งอะไรไป
การตรวจสอบตัวตนของเซิร์ฟเวอร์ปลายทาง
การตรวจสอบตัวตนของเซิร์ฟเวอร์ปลายทางของ NWS ทำโดยการใช้ประโยชน์จาก nostr โดยให้โหนดปลายทางปล่อย cert (TLS) บน nostr และเซ็นรับรองด้วยตนเองและอณุญาติให้ไคลเอนต์สามารถดึงใบรับรองนี้มาก่อนเชื่อมต่อกับโหนดที่เป็นจุดเริ่มที่เราใช้
และนอกจากนี้ในอนาคตของการพัฒนา NWS กำลังพัฒนาให้ NWS สามารถกำหนดให้โหนดปลายทางสามารถกำหนดค่าให้เข้าถึงอินเทอร์เน็ตได้ (ไม่ใช่แค่บริการภายใน) ทำให้ NWS ทำงานคล้าย VPN โดยสามารถเข้าเว็บไซต์ปกติได้ เช่น พิมพ์ "https google dot com" ก็เข้า google ได้
และทั้งหมดที่กล่าวไว้ข้างต้นเป็นเพียงการเริ่มต้น ยังมีคุณสมบัติอย่างอื่นอีกมากมายที่จะเข้ามาปรับปรุงปัญหาต่าง ๆ ในการใช้งานอินเตอร์เน็ต โดยส่วนตัวผมรู้สึกตื่นเต้นกับอนาคตของ NWS มาก ๆ และคาดหวังที่จะได้เห็นคนหันมาให้ความสนใจและใช้งานมัน ทั้งนี้หากใครอยากทดลองใช้งานก็สามารถติดตามได้ที่
GitHub: https://github.com/asmogo/nws
ส่งท้าย
สำหรับ series nOStr ผมตั้งใจจะหาเรื่องราวเกี่ยวกับ other stuff ที่น่าสนใจ ให้ทุกคน ๆ ได้ศึกษาไปพร้อม ๆ กัน เพราะว่า nostr ไม่ได้มีแค่โน๊ต
-
-
 @ 4ba8e86d:89d32de4
2024-10-24 23:36:47
@ 4ba8e86d:89d32de4
2024-10-24 23:36:47OP_CAT é um opcode simples, mas poderoso, que combina dois valores de entrada em uma saída. Originalmente, ele foi desativado devido a preocupações com problemas de memória, mas as condições mudaram. OP_CAT é um opcode que lida com a concatenação de valores de entrada, unindo dois valores em um. Embora possa parecer simples à primeira vista, suas possibilidades são amplas e intrigantes.
Especificação
O opcode OP_CAT opera abrindo dois elementos da pilha, concatenando-os na ordem em que estão empilhados e empurrando o elemento resultante de volta para a pilha. Dada a pilha [x1, x2], onde x2 está no topo da pilha, o OP_CAT colocará x1 x2 na pilha, onde '' denota concatenação.
Implementação
cpp if (stack.size() < 2) return set_error(serror, SCRIPT_ERR_INVALID_STACK_OPERATION); valtype vch1 = stacktop(-2); valtype vch2 = stacktop(-1);
if (vch1.size() + vch2.size() > MAX_SCRIPT_ELEMENT_SIZE) return set_error(serror, SCRIPT_ERR_INVALID_STACK_OPERATION);
valtype vch3; vch3.reserve(vch1.size() + vch2.size()); vch3.insert(vch3.end(), vch1.begin(), vch1.end()); vch3.insert(vch3.end(), vch2.begin(), vch2.end());
stack.pop(); stack.pop(); stack.push_back(vch3);
Essa implementação é baseada na implementação do OP_CAT em elementos.
O valor de MAX_SCRIPT_ELEMENT_SIZE é 520 bytes.
Notas
O OP_CAT existia na base de código Bitcoin antes do commit "alterações diversas" 4bd188c que o desativou. A implementação original funcionava da seguinte forma:
cpp // (x1 x2 -- fora) if (stack.size() < 2) return false; valtype& vch1 = stacktop(-2); valtype& vch2 = stacktop(-1); vch1.insert(vch1.end(), vch2.begin(), vch2.end()); stack.pop_back(); if (stacktop(-1).size() > 5000) return false;
Essas informações detalhadas sobre a especificação e a implementação do OP_CAT esclarecem como ele funciona e como as operações são executadas.
OP_CAT não é uma novidade, sendo parte das instruções do Bitcoin Script em versões antigas. Foi desativado devido a preocupações de aumento exponencial de memória na pilha de elementos. No entanto, desde que foi desativado, um tamanho máximo de 512 bytes foi fornecido para elementos de pilha, e isso também é aplicado ativamente hoje no Tapscript, que é o Bitcoin Script na atualização Taproot. O problema daquela época realmente não se aplica aqui, pois um script que desejasse criar elementos acima desse limite seria simplesmente inválido.
OP_CAT possibilita novas opções de assinatura, assinaturas Lamport com segurança quântica, cofres Bitcoin e convênios/CTV que determinam as condições de saída. Isso abre portas para métodos de escalonamento , Confirmação instantânea de transações on-chain , Livre mercado de sidechains, como Ark, e simplifica a implementação de BitVM para contratos inteligentes.
Várias aplicações possíveis para o OP_CAT, como covenants, verificação de provas SPV, proteção contra gastos duplos em transações não confirmadas, tornar o BitVM mais eficiente, realizar aritmética com números grandes, criar vaults e assinaturas resistentes a computadores quânticos.
Para reintroduzir o OP_CAT, seria necessária uma atualização (soft fork) nas regras de consenso do Bitcoin, o que exige planejamento cuidadoso. No entanto, a proposta atual é gerenciável e não apresenta as preocupações anteriores devido às limitações estabelecidas.
O OP_CAT promete ser uma adição valiosa à linguagem de script do Bitcoin, proporcionando um leque de possibilidades interessantes para desenvolvedores e usuários. A reintrodução desse opcode parece promissora, oferecendo um equilíbrio entre esforço e casos de uso potenciais, e ainda há espaço para discussões sobre suas vantagens e desvantagens.
https://lists.linuxfoundation.org/pipermail/bitcoin-dev/2023-October/022049.html
https://lists.linuxfoundation.org/pipermail/bitcoin-dev/2023-October/022049.html
https://github.com/EthanHeilman/op_cat_draft/blob/main/cat.mediawiki
https://medium.com/blockstream/cat-and-schnorr-tricks-i-faf1b59bd298
https://gist.github.com/RobinLinus/9a69f5552be94d13170ec79bf34d5e85
-
 @ 4ba8e86d:89d32de4
2024-10-24 23:30:46
@ 4ba8e86d:89d32de4
2024-10-24 23:30:46Com o Boltz, os usuários podem trocar perfeitamente seus bitcoins entre camadas, por exemplo. usar produtos financeiros avançados ou gerenciar a liquidez de seus canais relâmpago. Os Boltz Swaps não têm custódia, o que significa que os usuários podem sempre ter a certeza de ter controle total de seu bitcoin durante todo o fluxo de um swap.
Swap da Lightning Network (LN) para Bitcoin Onchain utilizando a plataforma Boltz.
Basta acessar o site Onion da Boltz:
http://boltzzzbnus4m7mta3cxmflnps4fp7dueu2tgurstbvrbt6xswzcocyd.onion/
Também é possível visitar o site oficial em:
https://boltz.exchange/
https://nostrcheck.me/media/public/nostrcheck.me_4413004608613998691706870605.webp
https://nostrcheck.me/media/public/nostrcheck.me_6400873373279640511706870649.webp
Primeiro, selecione qual tipo de Swap deseja realizar, por exemplo, você pode escolher LN para Bitcoin Onchain. Em seguida, insira o endereço Onchain de sua carteira. Após isso, basta efetuar o pagamento da fatura LN com o valor necessário e o Swap será concluído com sucesso!
Criar Atomic Swap. O pagamento inclui taxas de serviço de rede e boltz Enviar Mín .: 50.000 , Máx .: 1.000.0000
Para melhorar a resistência à censura e a privacidade, o Boltz não está disponível nas lojas de aplicativos, mas pode ser instalado como Progressive Web App (PWA) em todos os dispositivos Android e iOS, bem como em computadores desktop.
Como instalar o Boltz como App PWA.
Android.
-
Abra https://boltz.exchange/ em um navegador móvel como chorme ou Vanadium abra o menu do navegador e toque em "Instalar aplicativo": https://nostrcheck.me/media/public/nostrcheck.me_6529645890412951071706872223.webp
-
Confirme em "Install": https://nostrcheck.me/media/public/nostrcheck.me_1285765778020048231706872279.webp
-
Agora você encontra o Boltz como ícone do aplicativo na tela inicial, que pode ser usado como qualquer outro aplicativo.
iOS
-
Abra https://boltz.exchange/ em seu navegador móvel Safari e toque no botão de compartilhamento https://nostrcheck.me/media/public/nostrcheck.me_6654634165994432521706871151.webp
-
Toque em "Adicionar á tela incial ": https://nostrcheck.me/media/public/nostrcheck.me_4387192956979181391706871163.webp
-
Confirme tocando em "adicionar ": https://nostrcheck.me/media/public/nostrcheck.me_1403675023106875721706871174.webp
-
Agora você encontra o Boltz como ícone do aplicativo na tela inicial, que pode ser usado como qualquer outro aplicativo.
Desktop
- Aqui está um exemplo de como instalar o Boltz como aplicativo em um computador desktop Ubuntu usando Chromium: Abra https://boltz.exchange/ e clique no ícone de instalação que aparece automaticamente:
https://nostrcheck.me/media/public/nostrcheck.me_3169379622874819051706871546.webp
-
Confirme clicando em "Install": https://nostrcheck.me/media/public/nostrcheck.me_3547123478071766331706871554.webp
-
Agora você encontra o Boltz como ícone do aplicativo em sua coleção de aplicativos: https://nostrcheck.me/media/public/nostrcheck.me_3356870245715316401706871564.webp
Também pode executá-lo localmente:
Incentivamos nossos usuários técnicos a verificar o código e executar o aplicativo da web localmente a partir da fonte, seguindo as instruções abaixo.
Dependências.
Certifique-se de ter o Node.js LTS e NPM mais recente instalado. Recomendamos usar o nvm para gerenciar instalações do npm: nvm install --lts
Execução.
Clone o repositório, mude para a pasta do projeto e execute " npm install " para instalar todas as dependências. Em seguida, execute " npm run mainnet " e " npx serve dist " para iniciá-lo.
Abra: http://localhost:3000
no seu navegador e comece a trocar!
https://github.com/BoltzExchange/boltz-web-app#run
https://docs.boltz.exchange/
-
-
 @ 6ad3e2a3:c90b7740
2024-09-11 15:16:53
@ 6ad3e2a3:c90b7740
2024-09-11 15:16:53I’ve occasionally been called cynical because some of the sentiments I express strike people as negative. But cynical, to me, does not strictly mean negative. It means something more along the lines of “faithless” — as in lacking the basic faith humans thrive when believing what they take to be true, rather than expedient, and doing what they think is right rather than narrowly advantageous.
In other words, my primary negative sentiment — that the cynical utilitarian ethos among our educated classes has caused and is likely to cause catastrophic outcomes — stems from a sort of disappointed idealism, not cynicism.
On human nature itself I am anything but cynical. I am convinced the strongest, long-term incentives are always to believe what is true, no matter the cost, and to do what is right. And by “right,” I don’t mean do-gooding bullshit, but things like taking care of one’s health, immediate family and personal responsibilities while pursuing the things one finds most compelling and important.
That aside, I want to touch on two real-world examples of what I take to be actual cynicism. The first is the tendency to invoke principles only when they suit one’s agenda or desired outcome, but not to apply them when they do not. This kind of hypocrisy implies principles are just tools you invoke to gain emotional support for your side and that anyone actually applying them evenhandedly is a naive simpleton who doesn’t know how the game is played.
Twitter threads don’t show up on substack anymore, but I’d encourage you to read this one with respect to objecting to election outcomes. I could have used many others, but this one (probably not even most egregious) illustrates how empty words like “democracy” or “election integrity” are when thrown around by devoted partisans. They don’t actually believe in democracy, only in using the word to evoke the desired emotional response. People who wanted to coerce people to take a Pfizer shot don’t believe in “bodily autonomy.” It’s similarly just a phrase that’s invoked to achieve an end.
The other flavor of cynicism I’ve noticed is less about hypocrisy and more about nihilism:
 I’d encourage people to read the entire thread, but if you’re not on Twitter, it’s essentially about whether money (and apparently anything else) has essential qualities, or whether it is whatever peoples’ narratives tell them it is.
I’d encourage people to read the entire thread, but if you’re not on Twitter, it’s essentially about whether money (and apparently anything else) has essential qualities, or whether it is whatever peoples’ narratives tell them it is.In other words, is money whatever your grocer takes for the groceries, or do particular forms of money have qualities wherein they are more likely to be accepted over the long haul? The argument is yes, gold, for example had qualities that made it a better money (scarcity, durability, e.g.) than say seashells which are reasonably durable but not scarce. You could sell the story of seashells as a money (and some societies not close to the sea used them as such), but ultimately such a society would be vulnerable to massive inflation should one of its inhabitants ever stroll along a shore.
The thread morphed into whether everything is just narrative, or there is an underlying reality to which a narrative must correspond in order for it to be useful and true.
The notion that anything could be money if attached to the right story, or any music is good if it’s marketed properly is deeply cynical. I am not arguing people can’t be convinced to buy bad records — clearly they can — but that no matter how much you market it, it will not stand the test of time unless it is in fact good.
In order to sell something that does not add value, meaning or utility to someone’s life, something you suspect they are likely to regret buying in short order, it’s awfully useful to convince yourself that nothing has inherent meaning or value, that “storytelling is all that matters.”
I am not against marketing per se, and effective storytelling might in fact point someone in the right direction — a good story can help someone discover a truth. But that storytelling is everything, and by implication the extent to which a story has correlates in reality nothing, is the ethos of scammers, the refuge of nihilists who left someone else holding the bag and prefer not to think about it.
-
 @ 4ba8e86d:89d32de4
2024-10-24 23:20:51
@ 4ba8e86d:89d32de4
2024-10-24 23:20:51VeraCrupt foi lançado em 2013 como um fork do projeto TrueCrypt descontinuado. Desde então, o VeraCrypt tem passado por diversas atualizações e melhorias de segurança, incluindo a correção de problemas identificados por auditorias de código do TrueCrypt. O VeraCrypt inclui implementações otimizadas de funções criptográficas de hash e cifras, o que aumenta o desempenho em CPUs modernas. O software permite criar e gerenciar volumes criptografados em computadores ou dispositivos de armazenamento externo, com suporte para vários algoritmos de criptografia e recursos adicionais, como proteção contra ataques de keylogger e ocultação de volumes , tem opção de segurança robusta para proteger seus dados.
Quando você cria um volume criptografado no VeraCrypt, o software cria um arquivo virtual que funciona como um disco rígido criptografado. Esse arquivo é montado como uma unidade lógica no seu sistema operacional e pode ser acessado como qualquer outro disco rígido.
Antes que você possa acessar o volume criptografado, você precisa fornecer a senha correta. A senha é usada para desbloquear o arquivo virtual criptografado e permitir que o sistema operacional acesse o conteúdo. O VeraCrypt suporta vários algoritmos de criptografia, incluindo AES, Serpent e Twofish, que podem ser selecionados pelo usuário ao criar o volume criptografado.
O VeraCrypt também oferece recursos adicionais de segurança, como proteção contra keyloggers, que podem registrar as teclas digitadas no teclado para capturar senhas. Ele faz isso fornecendo uma interface virtual para digitar senhas, o que impede que os keyloggers capturem a senha real. O VeraCrypt também permite ocultar volumes criptografados dentro de outros volumes criptografados, o que fornece uma camada adicional de segurança.
O veracrypt proteger informações confidenciais armazenadas em dispositivos de armazenamento, como discos rígidos, unidades flash USB e cartões de memória, contra acesso não autorizado. Se um usuário estiver executando o Tails a partir de uma unidade flash USB, e o disco rígido estiver criptografado com o VeraCrypt, o Tails não terá acesso ao conteúdo do disco rígido, a menos que o usuário monte o volume criptografado do VeraCrypt e forneça a senha correta.
No entanto, é importante lembrar que a criptografia do disco rígido por si só não garante a segurança completa do sistema. Os usuários também devem tomar outras medidas de segurança, como manter o sistema operacional e o software atualizados, usar senhas fortes e não compartilhá-las com ninguém, e tomar cuidado com o acesso físico ao computador ou dispositivo de armazenamento externo.
https://veracrypt.fr
https://github.com/veracrypt/VeraCrypt/
-
 @ ee11a5df:b76c4e49
2024-09-11 08:16:37
@ ee11a5df:b76c4e49
2024-09-11 08:16:37Bye-Bye Reply Guy
There is a camp of nostr developers that believe spam filtering needs to be done by relays. Or at the very least by DVMs. I concur. In this way, once you configure what you want to see, it applies to all nostr clients.
But we are not there yet.
In the mean time we have ReplyGuy, and gossip needed some changes to deal with it.
Strategies in Short
- WEB OF TRUST: Only accept events from people you follow, or people they follow - this avoids new people entirely until somebody else that you follow friends them first, which is too restrictive for some people.
- TRUSTED RELAYS: Allow every post from relays that you trust to do good spam filtering.
- REJECT FRESH PUBKEYS: Only accept events from people you have seen before - this allows you to find new people, but you will miss their very first post (their second post must count as someone you have seen before, even if you discarded the first post)
- PATTERN MATCHING: Scan for known spam phrases and words and block those events, either on content or metadata or both or more.
- TIE-IN TO EXTERNAL SYSTEMS: Require a valid NIP-05, or other nostr event binding their identity to some external identity
- PROOF OF WORK: Require a minimum proof-of-work
All of these strategies are useful, but they have to be combined properly.
filter.rhai
Gossip loads a file called "filter.rhai" in your gossip directory if it exists. It must be a Rhai language script that meets certain requirements (see the example in the gossip source code directory). Then it applies it to filter spam.
This spam filtering code is being updated currently. It is not even on unstable yet, but it will be there probably tomorrow sometime. Then to master. Eventually to a release.
Here is an example using all of the techniques listed above:
```rhai // This is a sample spam filtering script for the gossip nostr // client. The language is called Rhai, details are at: // https://rhai.rs/book/ // // For gossip to find your spam filtering script, put it in // your gossip profile directory. See // https://docs.rs/dirs/latest/dirs/fn.data_dir.html // to find the base directory. A subdirectory "gossip" is your // gossip data directory which for most people is their profile // directory too. (Note: if you use a GOSSIP_PROFILE, you'll // need to put it one directory deeper into that profile // directory). // // This filter is used to filter out and refuse to process // incoming events as they flow in from relays, and also to // filter which events get/ displayed in certain circumstances. // It is only run on feed-displayable event kinds, and only by // authors you are not following. In case of error, nothing is // filtered. // // You must define a function called 'filter' which returns one // of these constant values: // DENY (the event is filtered out) // ALLOW (the event is allowed through) // MUTE (the event is filtered out, and the author is // automatically muted) // // Your script will be provided the following global variables: // 'caller' - a string that is one of "Process", // "Thread", "Inbox" or "Global" indicating // which part of the code is running your // script // 'content' - the event content as a string // 'id' - the event ID, as a hex string // 'kind' - the event kind as an integer // 'muted' - if the author is in your mute list // 'name' - if we have it, the name of the author // (or your petname), else an empty string // 'nip05valid' - whether nip05 is valid for the author, // as a boolean // 'pow' - the Proof of Work on the event // 'pubkey' - the event author public key, as a hex // string // 'seconds_known' - the number of seconds that the author // of the event has been known to gossip // 'spamsafe' - true only if the event came in from a // relay marked as SpamSafe during Process // (even if the global setting for SpamSafe // is off)
fn filter() {
// Show spam on global // (global events are ephemeral; these won't grow the // database) if caller=="Global" { return ALLOW; } // Block ReplyGuy if name.contains("ReplyGuy") || name.contains("ReplyGal") { return DENY; } // Block known DM spam // (giftwraps are unwrapped before the content is passed to // this script) if content.to_lower().contains( "Mr. Gift and Mrs. Wrap under the tree, KISSING!" ) { return DENY; } // Reject events from new pubkeys, unless they have a high // PoW or we somehow already have a nip05valid for them // // If this turns out to be a legit person, we will start // hearing their events 2 seconds from now, so we will // only miss their very first event. if seconds_known <= 2 && pow < 25 && !nip05valid { return DENY; } // Mute offensive people if content.to_lower().contains(" kike") || content.to_lower().contains("kike ") || content.to_lower().contains(" nigger") || content.to_lower().contains("nigger ") { return MUTE; } // Reject events from muted people // // Gossip already does this internally, and since we are // not Process, this is rather redundant. But this works // as an example. if muted { return DENY; } // Accept if the PoW is large enough if pow >= 25 { return ALLOW; } // Accept if their NIP-05 is valid if nip05valid { return ALLOW; } // Accept if the event came through a spamsafe relay if spamsafe { return ALLOW; } // Reject the rest DENY} ```
-
 @ bf95e1a4:ebdcc848
2024-09-11 06:31:05
@ bf95e1a4:ebdcc848
2024-09-11 06:31:05This is the lightly-edited AI generated transcript of Bitcoin Infinity Show #125. The transcription isn't perfect, but it's usually pretty good!
If you'd like to support us, send us a zap or check out the Bitcoin Infinity Store for our books and other merchandise! https://bitcoininfinitystore.com/
Intro
Luke: Paolo, Mathias, welcome to the Bitcoin Infinity Show. Thank you for joining us.
Paolo: Thank you for having us.
Knut: Yeah, good to have you here, guys. We're going to talk a bit about Keet and Holepunch and a little bit about Tether today, aren't we?
Luke: Sounds like that's the plan. So thank you again, both for joining us.
Introducing Paolo and Mathias
Luke: would you both mind giving a quick introduction on yourselves just so our listeners have the background on you
Paolo: Sure, I'm Paolo Arduino, I'm the CEO at Tether. I started my career as a developer, I pivoted towards more, strategy and execution for, Tether and Bitfinex. And, co founded with Matthias, Holepunch, that is, building very, crazy and awesome technology, that is gonna be disrupting the way people communicate.
Luke: And, Mathias, over to you.
Mathias: Yeah, thank you. Yeah, I've been, so I come from a peer-to-peer background. I've been working with peer-to-peer technology. The last, I always say five, but it's probably more like 10 years. I did a lot of work on BitTorrent and I did a lot of work on JavaScript. and a little bit later to, Bitcoin and I saw a lot of potential on how we can use Bitcoin with pureology and like how we can use.
P2P technology to bring the same mission that Bitcoin has, but to all kinds of data, setting all data free and, making everything private per default and self sovereignty and that kind of thing. I'm very into that. and I've been lucky to work with, like I said, with Paolo for, many years now and, Get a lot of, valuable, feedback and, idea sharing out of that.
And we're on a mission to, build some, really cool things. In addition to all the things we've already been building. So it's super exciting and glad to be here.
Luke: Oh, fantastic.
Introduction to Holepunch
Luke: Matthias, that was a perfect segue into basically, an introduction to, can you tell us about, Holepunch.
What is Holepunch and what are you doing?
Mathias: Yeah, sure. like I said, we co founded the company a couple of years ago. Now, we've been building up a team of really talented peer to peer engineers. we're always hiring also. So if anybody's listening and want to join our mission, please, apply. we have some really smart people working with us.
but we teamed up to basically. like I said in my introduction, I've been working on peer to peer technology for many years now and thinking ahead how we can, stop using all that technology when I started it was only used for basically piracy. I'm from the Nordics, and I think Knut is from the Nordics also, so he knows all about, the Nordics know about piracy.
It wasn't back in the day. A lot of very interesting technologies came out of that. But basically, how can we use those ideas that were proven by piracy back then to be really unstoppable, because a lot of people wanted to stop it, but apply that same kind of mindset to the general data, so we can build actual applications that has that kind of quality, that can withstand the wrath of God.
that can work without any centralization. Actually, nobody can shut down, not even the authorities if they wanted to. Basically unkillable and make that general enough that it can basically run any kind of application, solve a lot of really hot problems. it works on your own computers, your own networks.
Mobile phones, and tie that up. I'm a developer by heart, into a software stack that people can just build on. So not everybody has to go in and tackle all these problems individually, but just give them some software to solve all this so they can, as much as possible, just worry about making really cool applications that we use,
Yeah, like I said, we've been working really intensely on this, for a long time and in Holepunch, we made this our co mission to scale this up and, deliver a software stack on that. it's been really exciting and it's been really fun and it's been very, challenging, but if it's not challenging, then why, do it?
and, especially, with the backing of, Tether, through Paolo and also just expertise from there, we have a good hand built to deliver this to the world. And, the first thing we did was, like, think about what's, a good first application that we can build that can showcase this, but also something we really want to use ourself and see scale have also have on the world.
And obviously that was a communications app, keyed, which we was our first project. And, we're still in beta and we're still lots of work to do. And we're still iterating that really heavily, but I like to show that you can build these kind of apps without any kind of. central points. and we released that also, like the first thing we released when we launched the company.
And like I said, we're still, building and still iterating it. A lot of fun. and then take the software stack from that, which we call the pair runtime and then split that out. So anybody else can build similar apps on top. With that same technology stack, and, yeah, that's, we launched that earlier this year also, and, it's been really exciting so far, and it's, I love going to work every day and solve, even though, you can see on my hair that it's not really good for, the head scratching, but, but, it's really fun, and it's really challenging, and it's interesting thing. goal as a company, basically to have that if we go out of business tomorrow, our technology continues to exist because we're not in the loop of anything. It's also sometimes really hard to explain that we don't have any, chip coins involved or any kind of limitations on the stack because we're basically engineering it not to be part of it, because that's the only way you can actually engineer these things that they can understand.
anything, super exciting and, encourage everybody to try to check it out.
Luke: we've both used Keet and I've certainly enjoyed the experience. I, think, the, basics of this, as I understand it, is that it's, entirely on both sides. The communicators end, or a group of communicators, it's all on their end, and the communication is entirely peer to peer, what is Keet really, what is the basics of Keet as, say, a product?
What is the easiest way that you would explain what it is?
The Vision Behind Keet
Mathias: But We're basically trying to just build a world class communications app that works to a large degree, like normal communication apps that you know, like Signal, Telegram, WhatsApp. Just with all the centralization tucked away, with all the costs of running it tucked away, and then adding all the features that also we can, because we're peer to peer
People don't care about technology. We loved it, but don't have that surface off too much to the user.
Just have the user use it as any other app, but then just have it be 100 percent private per default, 100 percent like no strings attached. It just works. if we get caught off by a. From the internet tomorrow, it will still work, that kind of thing, but deliver that in a way, and this is always our mission where users don't really need to worry about it.
It just works. And, it works the same way to a large degree as their other apps work, except obviously, there's no phone numbers and things like that. Very cryptographically sound and, but trying always not to bubble it up. And I think that's, so it's actually a really simple mission, but it's obviously really hard.
And that requires a lot of smart people, but luckily our users in a good way, don't need to be very smart about that.
Keet vs Nostr
Knut: Yeah, a quick one there. No strings attached starts with the letters Nostr, so is, Keet and Nostr, do they go mix well together or, is there an integration there between the two? I see a lot of similarities here.
Paolo: I tried to explain the differences between Kit and Nostr. I think Nostr is a very interesting protocol, but also is very, simple. the way I like to describe it is that, if you are familiar with the history of filesharing, Starting from the first one, super centralized, and then eventually every single step, you get to a decentralized platform.
And the last one, the most decentralized one, that is BitTorrent. the history of file sharing proved that every time you try to centralize something, it ends up badly, right? if you have any special node in the system that does a little bit more than others and requires more resources than others to run, that will end up badly.
You might end up in a small room with a lamp in your room. Point it to your face, and then everyone suddenly will stop running an indexer. That reminds me about Nostr structure. if you are building a peer to peer system, or if you are building a very resilient communication system, if you think about Nostr, you would imagine that if you have, 10 million or 100 million users, the number of relays would be probably less than the square root of the number of users.
So that surface, although a hundred million users is very, they're not attackable, right? But the surface of, the relays is much more attackable. look at what is happening with, the coin joinin platforms, right? very similar. the beauty of KIT versus Nostr is that in KIT you have number of relays is actually equal to the number of users because the users are their own relays.
and they can act as relays for others to, further their connectivity. That is how we think a technology that, has to be ready for the apocalypse and resilient to the wrath of God should, work. if you have, a log number of users or square root of number of users as relates, I don't think it's cool technology.
It will work better than centralized, Technologies like WhatsApp and so on, or Twitter, but eventually will not work when you will need it the most. Because the point is that we will not know what will happen when we will need this technology the most. Today, not for everyone, but the world is still almost at peace.
Things might unfold, in the future, maybe sooner rather than later. But when things unfold, you will need the best technology, the one that is truly independent, the one that is truly peer to peer. it's not really peer to peer if you have specialized relays, but where you have super peers randomly.
Luke: Yeah, the difference here, between the Realize and not having any other centralized infrastructure in the picture is certainly an interesting distinction. I hadn't heard anything about that you can act as a next connector or something like that.
Pear Runtime
Luke: So there's a couple of related things. I know there was an announcement about the, pair runtime, is that right? can you talk a little bit about that or any other, ways that this is growing in your whole, platform,
Mathias: Yeah, sure. so basically when we talk about ideas, internally, also from our software background, We want to solve a small problem that then can solve it for everybody. So
We want to build technology that can just send data around efficiently, so you can build any kind of app on top. We're all about modularity and taking these things to the extreme so we can repurpose it into any kind of application and other people can, get value out of it.
And, that's been our mission from the get go. So basically, like Paolo said, when we built Keed. We took all of these primitives we have, it's all open source on our GitHub, that can do various things, relay encrypted data in a way that's completely private, nobody can read it, and in a generalizable way, so it can run on any applications.
We have databases that can interpret, work with this data on device, but still in a way where nobody else knows what's going on, fully private, and we spent many years perfecting this, and it's still ongoing. And we, similar to like connectivity, it might seem really easy if you don't know what's going on that, connecting this computer to another computer and another place, but it's really hard because ISPs and, your internet providers, et cetera, they don't really want you to do that.
So there's a lot of firewalls involved that you have to work around to get around This is all really, hard problems that took a long time to solve.
But luckily, all of these are like generalizable problems where you just solve them once to a large degree, and then it's solved for everybody. If you put them in a modular framework where anybody can put the Legos together on top. And that's what we've been heavily invested in. And then as we were building Keed, we realized that Keete is just like 95 percent of these Lego blocks that are applicable for anything.
So why not take all this stuff, pack it up for free, we don't make any money on it. and an open source runtime that we're just giving away so other people can contribute to it, but also build their own apps. the more peer to peer apps the world has, the better from my point of view.
and document it and make it really easy to install. And I think actually Paolo said something interesting because as soon as you have, one point of centralization, you can always unravel it. coming from the Bitcoin days, I remember how quickly things can unravel. people went to jail for linking to things because authorities, when they crack down, really hard.
so if you have one weak spot, it will be taken advantage of at some point by somebody. And so even things like distributing updates to your software can be really hard because this often requires a central point, like you go to a website and you don't download it. And so all apps built on our runtime, for example.
It's distributed through the runtime, which is a little bit mind bending. So all apps are peer to peer data applications themselves, and the network doesn't care, which means that we can continue to distribute updates even, if everything gets shut down, you only need like a bootstrap for the first install when you get the app.
So we're thinking that in. At every level, because it's really, important to us to, basically learn from everything that happened in the past and then actually build things that are resilient. And we take this to a degree where I'm sure we could move 10 times faster if we just let go a little bit of that idea, because it is easier to just put all the data in one place or put all the updates in one place.
But then it's then we're just building the same old thing that's going to die eventually anyway. So we're very, uncompromising in that mission of actually decentralizing everything from updates to data, and then also always solving in a way where everybody can take advantage of that.
And then the final thing I'll say about that is that, every time we update. That runtime, those building blocks of that runtime, every time we fix a bug, every time we make it faster, every app becomes faster. That's also very exciting. It's because you're building the whole infrastructure into this layer that runs on your phone.
And it's all somewhat generalizable. Every time we fix something, it's just better for the entire ecosystem. And that's obviously really, exciting. And like I said, actually, no strings attached.
Yeah, so I think you were referring to the trial of the Pirate Bay people there In Sweden, right? lucky enough to meet a couple of them in Denmark and it's been very fun to hear about their journey and, yeah, like
Knut: and there, there's, there was a great documentary made about it called TPBAFK. So the Pirate Bay Away From Keyboard, about that whole trial and how, corrupt the system was even back then. And, throwing people in jail for providing links. they didn't do any more wrong than Google did, from a certain perspective.
And, I remember even, before BitTorrents, there was a program called. DC or Direct Connect Do you remember that?
Mathias: I used to, it was one of my first introductions to decentralization. it as you just shared your, like a Google Drive for everyone or something. Like you just shared parts of your file tree to everyone who wanted to peek into it, Yeah, anyway. Oh, that's good that you didn't know you were going with that. it interesting what you said, because I think it's interesting to think that I think to a large degree, the whole decentralization movement that was happening with BitTorrent back in the day got shut down because At some point, authorities figured out that they could just block DNS requests to shut it down for normal people, and as soon as they did that, it was actually effective.
And to Paolo's point, no matter how weak it is, they're done. and they tried to kill the technology elsewhere, but that's actually what killed them. Then, obviously, alternatives came that people could pay for, and it also shows that people actually want, to stay on the right side of things.
I think, now it's going very much in the wrong direction again, because now we're back at abusing that centralization again. the cycle will repeat. But, yeah, like any point of weakness will be attacked at any point.
Decentralization vs. Centralization
Luke: So what are the drawbacks to decentralization? I think we and our audience certainly understand the benefit of decentralization, what you gain by decentralizing, but what do you naturally give up in terms of the user experience and the convenience factor?
Mathias: yeah, I'm sure Paola has stuff to say here, but I'm just, I love talking about this stuff, so I'll go first. Mattias.
I think it's a really interesting question, first of all, because it's one of those questions where You know, obviously I want to say there's no drawbacks, but like anything, it's a balance, right?
Because it's not that there's drawbacks and advantages, there obviously is, but it's also just a different paradigm. first of all, with sensitization, I think one of the biggest thing I noticed also with developers is that we all come out of systems, education systems. That teaches how to think centralized, which makes us biased towards centralized solutions.
and that's, I remember my whole curriculum was about servers and clients and stuff like that. it's actually really hard to think about decentralization as a developer. And I think that's actually part of why a lot of people think it's hard. It's complex because it is complex, but also because we're just like, we've been trained massively in the other direction, and it's really hard to go back because decentralization can be as simple as what Knut said about DC Connect, DC where it's just, oh, I'm just browsing other people's computers.
That's amazing. That's a really, simple experience, and it's like something you can never do But like in today's world, people, the first thing I always get asked is like, how do I get a username? And I'm like, usernames have an inherent centralization and there's trade offs there.
And we need to think that through and stuff. and most applications don't necessarily require usernames. I'm not saying that's a bad feature, but it's that's where you need to think more about the trade offs because there's governance involved to some degree. But for the core experience, and I think that's what we've shown in Keith so far.
Then, there's obviously tons of upsides also, it's much easier to do big data transfers. Money is less of a concern, which actually changes the thinking, how you think about features.
And that, again, is something we've been trained in a lot as developers, because we think centralized. When we talk about features at Holepunch, hey, we should add podcast recording to Keed. Normally somebody would say, that's going to cost a lot of money to host that data. And we just always we don't even have that discussion because it doesn't matter because it's just between the users.
And then it's more about like the UX. But then other simple, like I said, other simple discussions, let's add a username index. That's where we're like, okay, let's think that through because there's like various things to think about there because there's no centric governance, and we don't want to introduce that because again, one point is.
It's bad. so it's, more like you really need to think differently and it's really hard to wire your brain to think differently. but once you get past that point, I think it's, super interesting. And I, think actually developers care way more than normal people because, developers care a lot about how links look and links and structure and that.
And normal people are just used to just clicking buttons and apps and going with the flow on that. And that's also what we're seeing, I think, with, a lot of key
Paolo: I think the hiring has proven a little bit more challenging, as Matthias was saying, when you are told that the cloud is your friend, hosting, on, Google Cloud or AWS is the right thing to do. And, of course, it got cheaper and cheaper, so now everyone can host their websites.
But the reality is that 70 percent of, the entire internet knowledge is hosted in the data centers of three companies. developers should think about that, should think about the fact that internet was born to be point to point and peer to peer. And, we are very far away from that initial concept.
over the years, especially with the boom in, in the year 2000 for the internet boom, and bubble, then, realized that, holding people's data is the way to go, with social media and social network. That is even worse. And so you have these friendly advertisements that are telling you, That, with a smiley face that, you know, yeah, you should, upload all your data on, Apple cloud or Google cloud.
And in general, cloud backups are great, right? You want to have some sort of redundancy in your life, but the reality is that you should be able to upload those. In an encrypted way, and yet most of this data sits unencrypted because, the big tech companies have to decrypt it and use it for, to milk the information to pay for, for, another month of their new data centers.
the, issue is, we have so much power in our hands through our phones. the phones that we have today are much more powerful than the phones that we, or even the computers that we have 10 years ago or 5 years ago. And so We should, we are at a stage where we can use this hardware, not only for communicating, but also for in the future for AI processing and inference and so on.
is, we need to, understand that the word cannot be connected to Google. I mean we cannot be a function of Google. We cannot be a function of AWS. And so I think that, there is, escalating pace of, towards centralization and it's almost a black hole.
And eventually, the, we'll attract all the lights and if we are too close to it, no lights will come out anymore. And, that's why we want to really to double down on this technology, because it's not going to be easy, right? It's going to be very challenging, and most of the people don't care, as Maite has said before.
Most of the people will think, everything works with WhatsApp and, Signal, but Signal announced that their 2023 costs for data centers and data center costs are around 50 million, and they, apart from the mobile coin that was not The best thing that they could do, there is, it's not easy for them to monetize.
And the problem is that if you are, you're basically almost the only way to monetize it is to sell your customer's data. So if you don't want to sell your customer data, eventually your service will not be sustainable. So the only way to make it sustainable is actually going back to peer, where you can leverage people, infrastructure, people, connectivity, people, phones, people, processing power, Deliver very high quality communication system.
And when they will care, it will be probably usually too late if nothing exists yet. when people will care is because shit is hitting the fan. And, you really want to have a solution that is not, that will survive if, the countries around you or around the country where you live are not going to be nice to your own country.
So that's the view to peer-to-peer. The peer-to-peer wheel system will keep working if your neighbor countries are not going to be nice towards you. That's independence, that's resiliency, those are terms that, we need to take very seriously, especially seeing where the, world is going to.
Knut: Yeah, I think we're all primed for, centralized solutions, from a very young age. this is the state, this is what it is like, state funded schooling. state funders or state subsidized media. We are, like brainwashed into, trusting, institutions all our lives.
So I think that is somewhat connected to why people are so reluctant to be vigilant about this on the internet. I think the two go hand in hand that we, take the comfortable way, or most people take the comfortable route of, not taking responsibility for their own stuff. not only on the internet, but outsourcing responsibility to the government is basically the, another side of the same coin, right?
Mathias: I also find it very interesting, especially being from a small country like Denmark that doesn't have a lot of homegrown infrastructure. And I'm just seeing how much communication with some of the public entities is happening through centralized platforms like Facebook and things like that, where even though we centralize it, we also centralize it in companies that we don't even have any control over in different countries where we probably have, no rights at all.
So it's like hyper centralization, especially from the weakest point of view. And I think that's super problematic. And I'm always. Thinking it's, weird that we're not talking about that more especially when you look at the things that they're trying to do in the EU, they're almost trying to just push more in that direction, which I find even more interesting.
yeah, definitely. it's, a huge problem and it's only getting bigger. And that's, why
Challenges and Future of Decentralization
Luke: So to what level can decentralization actually get there? What is the limit to decentralization? And I'll calibrate this with an example. The internet itself, you said it was built to essentially originally be decentralized, but we don't have it. For physical links, like individual physical links between each other, the fiber or whatever the wire is goes together into another group of wires, which eventually go into some backbone, which is operated by a company.
And then that goes into the global Internet. And so somewhere it centralizes into telecom companies and other services. It might be decentralized on one level, but there is a layer of centralized services that make the internet work that isn't necessarily the so called cloud providers and that sort of thing.
So is there a limitation to how far this can go?
Paolo: I think the, in general, sure, there are the ISPs and, their physical infrastructure is in part centralized, but also you start having redundancy, right? So for example, the backbones are redundant. There are multiple companies running, cross connects across different areas of the world.
Now you have Starlink if you want. that is a great way to start decentralizing connectivity because Starlink will not be the only one that will run satellites, so there will be multiple companies that will allow you to connect through satellites, plus you have normal cabling.
So you will have, it will become a huge mesh network, it's already in part, but it will become more and more a huge mesh network. in general, you will always find a way, even with a pigeon, to start sending bits out of your house.
I think the most important part is, you have to be in control of your own data, and then, you need to send this data with the shortest path to the people that you want to talk to. Right now, I usually make this example, because I think it's When we do this presentation, we try to make people think about how much waste also centralized systems have created.
imagine you live in Rome, you live in Rome and you have your family. Most people live nearby their families. That is a classic thing among humans. 90 percent of the people live nearby their families. Maybe nearby, like 10km, 50km nearby. If you talk to your family, every single message, every single photo that you will send to your family, that message will travel, instead of going 50 kilometers in a nearby town where your mother lives or your father lives, it will travel every single message, every single bit of every single video call or every single bit of every photo will travel 5, 000 miles to Frankfurt just to go back 50 kilometers from you.
Imagine how much government spent in order to create these internet lines and to empower them to make it bigger, more, with more capacity Peer to peer allows with a lower latency, allows to save on bandwidth, allows to save on cost of global infrastructure.
So that's how, actually, We can create better mesh networks, more resilient mesh networks, just because data will always find the shortest path from one point to another.
And still all roads lead to Rome. I'm Italian, so I need to use Rome as an example.
Knut: Yeah.
Mathias: I think the discussion here is really interesting compared to Bitcoin, because it's actually the scaling longer term. Sovereignty, like how, Bitcoin kind of told us very direct terms that if you have a key pair, you have your money.
And it doesn't matter where you are in the world. If you have that key pair, you have a way to get to that money. the means of transportation, it's actually very uninteresting in that sense, because you have it with you. The Internet today, the centralized Internet is designed in a way where, what does it mean to go to Facebook?
it's really hard to explain because it's like some certificate that issued by somebody, and there's. Some, cabal of companies that manages them, there's some regulations around it, but we don't really actually understand it that well as normal people. Technically, we can understand it, but it's very, centralized and it's very, opaque and it's built into the infrastructure in that way, in a bad way.
And, with Pure Technology, we're taking the same approach as Bitcoin here and saying, You're just a key pair, and the other person is just a key pair, and there's a bunch of protocols around that, but the transportation is actually not that interesting. Right now, we use the internet to do it.
We'll probably do that for a long time, but there's no reason why we can take the same technology we have right now and in 50 years run it on, laser beams or something else, because we're taking the software and feedback.
Bitcoin and Holepunch: Drawing Parallels
Mathias: I think, that's the main thing to think about in that. Discussion.
Luke: when, Paolo, when you were talking about that people don't care, when you were saying that people don't care because WhatsApp just works, I was at the same time thinking that's the parallel of people saying that, I don't care because Visa just works, right? And so the parallel between Bitcoin and what you're doing at Holepunch, Keet, everything else here, really seems to be tracking along the same line.
And I guess there's the connection that, I won't say all, but a lot of the people involved are already in the Bitcoin ecosystem. But can you comment on is there a little more of a connection there between Holepunch and Keet and Bitcoin?
Paolo: Yeah, Bitcoin definitely is working and servicing, I think, in a good way, many, people in communities. The users of Bitcoin today are, unfortunately, and also that relates to Tether, mostly, in the Western world, in the richer countries, as a way to save wealth and, as a store of value, more than a means of exchange.
For different reasons, right? We'd like a network that would improve, of course, over time, and there will be different approaches, but, still, the world is not yet using Bitcoin, but the world will use Bitcoin when shit will hit the fan. but the beauty of Bitcoin is that an option is already there, is available, and when something bad will happen, people immediately, with a snap of a finger, will turn to Bitcoin, and will have it and can use it. don't have that in communications. What is our communica our parallel with communications, if we don't have it? I don't know, because if, if suddenly centralized communications will, be blocked, then, or privacy in communications will be blocked, and you cannot, you cannot use Whatsapp, or Whatsapp has to start giving all the information to every single government.
and the government will become more evil than what they are today, also western governments then. don't, we wanted to build the exact parallel as we said it, we just tried to describe it, that with Bitcoin, for communications. We need to have something that, since there are so many alternatives that are working as with your, you can make the parallel with Visa, right?
Visa is working today, so people are still using a lot of Visa, but if something will happen, they will use Bitcoin from one day to another. Whatsapp is working, and Zoom is working, and Google Meet is working, so people don't feel the urge, but there will be a trigger point when people will feel the urge at some point in their lives, because something happened around them, and we need to make sure that kit will be available to them.
and will be an option, will be stable, will be well designed so that when they will need it the most that option will be available to them.
Luke: Yeah, fantastic.
The Future of Decentralized Communication
Luke: And so I think the follow up I have, and just to get back to the earlier discussion a little bit with Nostr, the communication in terms of messaging, I absolutely see that and directly in what Keet is, I already absolutely see that. Is there a goal to get somewhere towards more like Social media, social networking, things like that in a, in certainly a decentralized way, but right now there isn't something like that as I understand it, coming from, Keet.
So is, that a goal? Is that on the roadmap?
Paolo: Yeah, it is on the roadmap, it's something that, so we had to start with the thing that we thought was more urgent and also the thing that could have been, would have been a game changer. social media is very important, especially In difficult situation, you want to get news, and you want to get unbiased news, so you want to use, social networks to see what's happening in the world.
But we, think that the most sacrosanct thing that you need in your life is to be able to talk to your family and friends in any situation with the highest privacy possible. that's the first thing that we tackled, and also was a way to battle test the technology with, KIT you can do high quality video calls as well, so if we are able to tackle in the best way possible privacy and extreme scalability of peer to peer communications, then on top of that foundation we can build also social media and every single other application that we have in mind.
Mathias: But first, we wanted to tackle the hardest problem. No, I think it makes a lot of sense. And I also just want to say, as a, probably like one of the most prolific KEET users, I use KEET right now also as a very, like a social media, we have big public rooms where we talk about KEET and talk about technology. I get a lot of the value I would get otherwise on Twitter X from that because I, it's like a public platform for me to, get ideas out there, but also interact with users directly.
And I think, there's many ways to take them as a young app. And we're talking about this a lot, obviously it has to be simple, has to be parent approved. My parents can figure it out, but I think, to a large degree, all really healthy social networks that are actually, to some degree, a communication app.
And it's also just a really good way to get local news and to get this locality that Peter is good at. That doesn't mean that we might not also make other things, but I think it's a hard line to set the difference between a social network and a communications app when it's structured correctly,
Interoperability and User Experience
Luke: Yeah, and this, another thing that came to mind just as, you were talking about these parallels, as, I understand it, the account system with Keet is, essentially still just a, Key pair. Correct me if I'm, wrong,
Mathias: Very, true.
Luke: you backups with the same 1224 words.
Is, that fully interoperable as well? Is that, could be your Bitcoin key. That could be
Mathias: We use the, same, I can't remember the date, the BIP, but there's a BIP for like during key generation. So we can use it also in the future for other things. and you have those words, you have your account, and that's, we never store that. And that's like your sovereignty and, no, I was just going to say that lets you use it seamlessly on different devices also. It's one of those things that I love because I know what's going on when you use keyed Insanely hard problem, but it's solved by the runtime, and it just works seamlessly and I think that's, the beauty of it.
Paolo: I think there's some UX stuff to figure out about onboarding that stuff a little bit easier for normal people. That's probably to a large degree the same for Bitcoin. The other part that I would do with Bitcoin is that, with Bitcoin, with your 12, 24 words, you can access your private wealth. the beauty of Bitcoin is that you can remember 12 24 words, you cross borders, and you carry with you your wealth. You can do the same thing with your digital private life.
You remember 12 24 words, they could be the same by the way. whatever happens, you can spawn back your digital private life fully encrypted from, one of your other devices that you connected that is somewhere else in the world. So when you start seeing and understanding the unlock in terms of also human resilience that this creates is very, insane and can create a very powerful, that can be used for, to create a very, powerful applications, not just communications, but you can build.
Really any sort of interaction, even mapping. Imagine peer to peer mapping, where basically data is not stored in one single location. You can access, tiles of the maps, from, local people that curate them in a better way. So the, level of applications that you can build, All unlocked by the same technology that is being used by Bitcoin is very, incredible.
Luke: Yes, absolutely it is. And what do you think of the idea that all of this stuff is just interoperable now based on essentially you have your private key and there you go. It doesn't matter the technology stack. Is that sort of an agnostic thing where you can take your data to any one of these systems?
What you're building with Keith being one, Nostr being another, Bitcoin being a third, what do you think of that?
Paolo: Yeah, the fact that, data is yours, right? So you should do whatever you want with your data. That is, I think, an axiom that we should assume. And, it shouldn't even, we shouldn't even discuss about this, right? We are discussing about it because people are trying to take away this axiom from us.
The, you are a key pair, and you're basically, unique, and uniqueness is expressed by the cryptography around those 24 words, and that's, that also is a way to prove your identity, it's a mathematical way to prove your identity.
No one can steal that from you, of course, but no one can track it as no one can impersonate, should not be able to impersonate you. So it's truly powerful.
Mathias: also think it's like worth remembering here also in this discussion that a lot of very high valuable data for yourself is actually not that big, but centralized platforms take it hostage anyway. if you take all my chat history and, I have pictures, but like a couple of the pictures would probably be bigger than all my chat history ever.
but a lot of that, those messages have a lot of value for me, especially personally and also being able to search through it and have infinite history, it's very valuable for me personally. But it's very scary for me if that's on some other platform where it gets leaked at some point, et cetera, et cetera.
But we already have the devices, just normal consumer devices that we buy, that we all have, phones, computers, whatever, that have more than enough capacity to store multiple copies of this. In terms of like per user, data production, it's a manageable problem.
And I think it's interesting how, providers force us to think in terms of giving that data away, even though we could easily store it.
Paolo: And this is even more important when we think about potential, AI applications, right? So imagine your best assistant. Paolo's assistant should go through all my emails, my kids chats, my old social stuff, and be able to be my best assistant. But in order to do that, I have two options.
Either, I imagine that OpenAI would come with an assistant. They would upload, All the information on their servers, crunch that information, and then, use it to serve, me, but also service their own needs. And that can become very scary, also because they wear a hat. It's public, right?
you don't want your most intimate codes that your best personal assistant could know, to be on somewhere else, rather than your devices. And so people were, people never uploaded, at least most of the people would never upload medical, information on Facebook, right? But they are uploading it on ChatGPT to get a second opinion.
so things can be, get even scarier than what we described today because, we, discussed about social media, that is basically, the fun part where we upload photos, But, things can become scarier when it comes to privacy and data control with ai.
So I want to see a future where I have a local AI that can read all key messages that I have from my local phone on my local device, and can become the best powers assistant possible without renouncing to my privacy, and also still governed by the same 24 words. the fine tuning that is applied on that LLM should stay local to my own device, and it should be in control of that.
And still, the current power of the devices that we have makes it possible. We should not fall for the same lie. We don't need, of course, big data centers with GPUs are important for training a huge LLM, but that is a generic LLM. You can take that one and then fine tune it with your own data and run it by yourself.
And for most of it, unless you want to do crazy things, that is more than enough and can run on modern GPUs or local GPUs or your phones. We should start thinking that we can build local experiences without having an API all the time connected to someone else's data center.
Knut: Yeah.
The Role of Tether in the Crypto Ecosystem
Knut: It's super interesting. you briefly just briefly mentioned tether before and I think we need to get into this. what is it and how much of a maxi are you, Paolo?
And, what, made this thing happen? Can you give us the story here about Tether?
Tether's Origin and Evolution
Paolo: Tether started in 2014. I consider myself a maxi, but running Tether, you could say that, I'm a shit coiner. I don't mind, right? I like what I do, and I think I'm net positive, so it's okay. Tera was born in 2014 with a very simple idea. there were a few crypto exchanges in, 2014.
it was Bitfinex, Coinbase, Kraken, Bitstamp. OKCoin, there was BTCChina, and just a few others, right? Around 10 that were meaningful. The problem back then was to do, trading arbitrage, you sell Bitcoin on the exchange where the price is higher, you take the dollars. From that sale, you move the dollars on the exchange where the price is lower and rinse and repeat.
That is called arbitrage. It is a property of every single efficient financial system. And that also helps to keep the price of Bitcoin in line across different exchanges. But, that was very, hard in 2014. If you remember in 2013 was the first year that Bitcoin broke the 1, 000.
But on some exchanges the price was 1. 2, on others was 900. in order to arbitrage that price difference, you have to move dollars from one exchange to another and Bitcoin from one exchange to another. You can move Bitcoin from one exchange to another. 10 minutes, but dollars would take days, right?
International wires. And so of course the opportunity arbitrage was, fully gone by, the, time the wire was hitting the, receiving exchange. the reason why we created that was, USDT was simply to put the dollar on a blockchain so that we could have the same user experience that we had with bitcoin.
For the first two years, almost no exchange apart Bitfinex understood USDT. Then Poloniex in 2016 started to add the USDT across for against every single trading pair. There was the start of the ICO boom. 2017 was the peak of the ICO boom and, USDT reached 1 billion in market cap. Fast forward in 2020, we had around 10 billion in market cap, and then the bull run started, but also another important thing started, that was the pandemic.
USDT's Impact on Emerging Markets
Paolo: So the pandemic had a huge effect on many economies around the world, in all the economies around the world, but especially in emerging markets, developing countries.
Basically pandemic also killed entire economies. And so as a Bitcoin you would think, oh, all these people that are in countries like Argentina and Venezuela and Turkey and so on, they should use Bitcoin and they should, they should, only use Bitcoin because everything else is cheap.
So that is pretty much, the approach that we have as Bitcoiners that, I believe in. But the problem is that. Not everyone is ready, so not everyone has our time to understand Bitcoin. Not everyone has yet the full skill set to understand Bitcoin at this stage, at this moment in time.
we as Bitcoiners didn't build the best user experience in the world, right? So one of the best wallets for Bitcoin is still Electrum. That, is not necessarily nice and well done for and simple to be used for, a 70 year old lady. so we need to do a better job as Bitcoiners to build better user experiences we want Bitcoin to be more used around the world.
At the same time, 99 percent of the population knows, especially the ones that are living in high inflation areas, knows that there is the dollar that is usually Much better currency than what they hold in their hands. the US dollar is not, definitely not perfect. It's not the perfect fiat currency. but it's like the tale of the two friends running away from the lion, right?
you have, one friend tells to the other, Oh, the lion is gonna kill us. We have to run really fast. And one of the two friends says to the other, I just have to run faster than you, right? So the US dollar is the friend that is running faster, in a sense that is the one that is likely better than the others.
And so being better than the others is creating a sort of safety feeling among 5 billion people in the world that live in high inflation countries. And for those people that, they don't have yet the time, they didn't have the luck also, maybe, to understand Bitcoin, they are, in fact, using USDT.
If you live in Argentina, peso lost 98% against the US dollar in the last five years. The Turkish L lost 80% against the US dollar in, the last five years. So of course, Bitcoin would be better than the US dollar, but even already, if you hold the dollar, you are the king of the hill there, right?
So because it's, you are able to preserve your wealth much, better than almost anyone else in the region. I think, USDT is offering a temporary solution and is providing a service, a very good service to people that don't have alternatives and good alternatives and they are very, familiar with the U.
S. dollar already. so eventually, the hyperbitcoinization, I think it will happen. there is no way it won't happen. It's hard to pinpoint on a time when, that will happen. But it's all about the turning point. What the economy will look like in the next, 10, 20 years and what trigger point there will be for fiat currencies to blow up and become irrelevant.
Bitcoin as a Savings Account
Paolo: the way I see it is that it's likely that the U. S. dollar will stay around for a while, and people might still want to use, the U. S. dollar as a checking account, but they, should start to use, Bitcoin as their savings account, in the checking account, you, are happy to not make interest, It's something that you use for payments, it's something that you are okay to detach from because it's the money that you are ready to spend.
The savings account is the thing that we should fight for. This thing is the thing that matter the most, and, it's the thing that will is protecting people wealth. And so in the long term. And in the medium term, we should push for this savings account to be Bitcoin. also with Tether, we are heavily investing in companies, in Bitcoin companies.
we support the Blockstream. We supported so many in the space that are, we, are supporting RGB. That is a protocol that is building, assets on top of, like network, style channels. Thank you for listening. and we buy Bitcoin ourselves. We do a lot of Bitcoin mining.
We develop, I think, the best and most sophisticated Bitcoin mining software, by the way, based on hole punch technology. It's like IoT for Bitcoiners and Bitcoin mining. It's very cool. we are relying on the dollar and, you could say that USDT is helping the dollar, expansion, but the same way I don't think Dollar and Bitcoin aren't necessarily opposed to one or the other.
I think that Bitcoin has its own path. And no matter what happens, there is no way to slow it down. I think, it's going to be inevitable success. It's going to be inevitable that it will become global internet money and global words money. No country will trust to each other with, with each other currencies for, for a longer time, and so the only viable solution is a currency that is governed by math.
That is the only objective way, objective thing that we have in the universe. that's my train of thoughts on, Tether and Bitcoin.
Knut: Oh, thank you. Thank you for that explanation. It explains a lot of things. To me, it sounds a bit like you're a lubrication company, like selling lubrication for the transition between the rape of the dollar to the love fest of the hyperbitcoinized world, to make the transition a little smoother.
Paolo: we are more than, at Tether we have also this educational arm and, believe it or not, the majority of the creation we do is actually on Bitcoin, right? So we are supporting the Plan B network led by the great Giacomo Zucco. The unfortunate thing is that USDT, didn't have a marketing team up to, 2022 with Tether.
So basically, I wish I could say that success of Tether is because we were super intelligent and great. but actually the success of Tether, unfortunately is a symptom of the success of, of, national economies. And it's sad if you think about it, right? So the success of your main product U as it is, They're actually proportional to the FACAP of many central banks. And, but it is what it is, right? So we need to do what we do at, really, at DataRace, creating all these educational contents to try to explain that, sure, we are providing a tool for today, but, For tomorrow you probably need, you need to understand that you have other options, you need to understand Bitcoin, because as we said for, Keith, right?
So the moment when you will need the most Bitcoin, it has to be available, you need to understand it, so that is a true option for you. The way we, see bitcoin education.
Knut: No, and, something like Tether would have, emerged, either way, and it's very comforting to know that it's run by Bitcoiners and not by a central bank itself or something. yeah, and the Plan B Network, I was a guest lecturer there in Logano and it was fantastic.
I love what you're doing there with the educational hub. And we even got Giacomo to write the foreword to our new book here that you can see here behind Luke.
Luke: Always say the title, Knut. Always say the title.
Knut: Bitcoin, the inverse of Clown World. It's, you, if, you're good at maths and emojis, you might be able to figure out the title from the cover, but it's one divided by Clown World anyway, which is on the opposite side of the everything divided by 21 million equation, So anyway, looking forward to seeing you in Lugano and giving you both a copy of the book, of course.
Paolo: Oh, with pleasure, with great pleasure, with a nice, education.
Luke: Absolutely. Yep.
Plan B Forum and Future Events
Luke: 100%. And we have to wind things down, but I'll just say as well, yeah, absolutely looking forward to Lugano Plan B Forum. Always a highlight of the year. It was my first time last year. I absolutely loved it. can't wait to attend this year.
so it's the 25th, 2020 6th of October, 2024. this year, it's a Bitcoin event that is not made to make money. So the problem with events is that. You have to find sponsors, and usually, sponsor might not be well aligned with the message you want to give, right? I think Tether is lucky enough, to not have to make money on the event.
Paolo: I want to have, good, guests. I want to have great speakers. I want to have the messaging. That is not only about Bitcoin, it's about, freedom of speech as well. We had the family of Assange for the last few years, and I think that they will come also this year.
I'm going to be probably killed by the By our marketing team, I'm not sure if they announced it, but we are going to have another Plan B event also in El Salvador next year, so we're trying to create this network of cities and countries that have things in common and, invite people that want to share knowledge around the world.
And, yeah, and of course we, are very proud of the good food that we, serve in Lugano. So that is another thing that, not all the bands can say the same thing.
Knut: No, it's fantastic. And we happened to bump into the Assange family at the cocktail bar in a fancy hotel and, had a very interesting conversation with them there. So if you're listening. Anyone from the Assange family is welcome on the show any time. So yeah, no looking forward to that event for sure, we had a great time.
And I think we're even playing this year, aren't we, Luke?
Paolo: You're
Luke: yeah, the Satoshi Rakamoto is in the event there, we, played, back in Prague, it was my first, time, but Knut is a regular at the Rakamotos.
Yeah, we played at Lugano last year Oh, anything and everything, what did we do in Prague?
Knut: paranoid and,
Paolo: Can I commission a
Knut: What song would you like to hear?
Paolo: I have two that I would suggest. One is Nothing Else Matters.
Knut: Alright.
Paolo: So I think that, is very inspiring, right?
Knut: Bitcoin, for sure.
Nothing Else Matters. it's perfectly aligned with Bitcoin. And, the other one is Sad But True. Oh, that would be fun. We'll squeeze in some Metallica there, won't we, Luke?
Mathias: we'll 100% have those songs ready to go. We also have, a big peer to peer track at the conference,
Knut: Yeah.
Mathias: not so much music, but yeah, that's peer to
Knut: Nothing else matters.
Luke: looking forward to that.
Knut: Sorry, brain fart. Sad but true is about the dollar still being around,
Paolo: Yeah, you can say that.
Luke: Okay.
Final Thoughts and Closing Remarks
Luke: Hey, we have to wind things down here because, we're, almost, out of time. So I'll just hand this, back to you both. Is there anything else you'd like to, mention about, your plans in the upcoming couple of years, in, key, toll, punch, anything like that?
Mathias: only that we're, like I said, we're integrating really hard right now, and it's a really fun time to, join the company because, we're small and efficient We get to work with Tether, which has a lot of benefits and it's getting really fast, so definitely check that out. And it's also a really fun time to join Keith in our public rooms.
There's a lot of very personal, in a good way, intense chats where you get to be part of the loop. I love to be part of those early communities and I would suggest everybody to check that out and go to the website and try it out.
Paolo: we will certainly do that. Yeah, I couldn't agree more. So go check out Keith and Holepunch and the Plan B forum in Lugano, You could visit tether. io, that is, the website where we are trying to explain what we have in our minds between, finance, bitcoin mining, energy production, AI, communications, brain chips and stuff, right? I think it's more exciting.
Mathias: Just those things, that's all.
Paolo: Yeah, we can piss off more than this. Thanks.
Mathias: a
Luke: No, It's just perfect. and is on that note, is there anywhere else specific you'd like to direct our listeners?
Paolo: just follow the social channels and give us feedback on kit all the time because these technologies, needs everyone's help to be nailed them.
Mathias: We love technical feedback. We love UX feedback. We're trying to make something that works for the masses, so anything is good.
Luke: So that's, all at Keet. Is that correct? For Keet?
Mathias: Key. io and pairs. com for our runtime. It's all peer to peer.
Knut: Alright,
Mathias: Wonderful. And you're also still on the legacy social media platforms, right? Yeah.
Knut: we'll make sure to include links to your handles so people can find you there if they would like. forward to seeing you in Lugano.
Paolo: Likewise, I
Knut: But yeah, worth saying again.
Paolo: Thank you for having an invitation.
Luke: Yes, we'll wrap things up here. This has been the Bitcoin Infinity Show.
-
 @ bb0174ae:75f7239a
2024-10-24 21:23:55
@ bb0174ae:75f7239a
2024-10-24 21:23:55What is Cyphermunk House? It is everything that is unprovided. It is the education that is never taught. It is the culture that is never commissioned. It is the space for the community that was never allowed to flourish because an equitable economy was never allowed to grow. It is a space to BE YOUR OWN BANK and a space to STAY HUMBLE.
Cyphermunk House is London’s Bitcoin beacon. Providing sanctuary from the mainstream; from the politics of division, the brainwashing of legacy media, the predictive programming of film, the ‘three-quarter reptiles’ of music, the ‘shock value, indignation and existential angst’ of modern art and the centuries long corruption and exploitation of central banking. It is counter culture in extremis. A hotspot of no fear. A 21st space where fiat pastimes are secondary and pleb living is primary.
What is bitcoin? Cross the threshold. How do you obtain it? Take a seat. Want to stack? Let’s begin. Dive into the mathematics of hope, the code of change and the magic of self-sovereignty. In here we educate, providing knowledge to match the student whether you are a stone-cold newb or a humble stacktivist. In return we learn that there are still so many who are yet to realise that money is broken, issuance matters and a bitcoin can be divided into things called sats. In other words, there is work to be done.
Work that is evolving like that which inspires us. Can we educate? Can we provide space for people from all walks of life? Can we provide the seeds for discussion, the platform for ideas and the spectacle that confronts the issues in our society? Can we get a former Minister of State to laser eye his image?
So far, we are meeting these challenges, with more newbs through our doors than we could ever imagine, lured in by the rabbit of an upended banknote and their own curiosity. What the hell is that? And what's going on inside this rabbit warren of a building a mile’s crow flight from the life supported heart of British financial might.
The ‘what’ is huge. Education. Culture. Freedom. And community. That same orange cocktail that bitcoin is pouring all over the world. Standing in direct opposition to the trends of indoctrination, centralisation and isolation that have pushed the group to the fringe and questioned the very idea that humans are social beings. In our world, meetups, conferences and real-world spaces are thriving. Education is pleb-led and free. And our culture is king.
I have witnessed the artistic offerings of this capital a lifetime over; dance on rooftops, songs beneath the river and Shakespeare performed by a man and a cast of sheep. In three short decades I have worked across music, theatre, film and art, and now find myself at the helm of Cyphermunk House. What is being created within these walls is more inspiring and exciting than anything the Tate has ever shown me, or the West End, or the Dome. This is the edge of the cultural moment. Lightning sharp and electric.
Because our culture does more than entertain. It informs. And transforms. And it is happening everywhere, simultaneously. And in this tiny postcode of West Central London, it is happening hard. We are 'Privacy Defenders'. We will expose 'The Ugly Reality of War Crimes' and we will declare that 'Coin Mixing is My Right' and yours too as we work towards a 'Humanity in Consensus'. Inspired? Come along and chuck it on the walls in the paradise paint of a world being built from the ground up. For this is the culture of code and it will not be put back in the box.

And yes the space is temporary, six more months perhaps, but its temporality is tangible forever, nostr makes it so. Our records permanent, our doors always open. Always sharing knowledge, wisdom and advice. While in these moments of tangibility, these blocks of time in meters of space, we will fire up the beacons and summon the zaps, for bitcoiners, artists, outcasts and dreamers to the temporal dance of rebellion that burns behind these doors.
“In the same way El Salvador felt way ahead of its time – a nation state adopting bitcoin as legal tender. This feels like it’s a cycle too early too. Surely, we shouldn’t have something this good till the 6th epoch." - Si, Bitcoin Events UK
And when we close our doors and move to pastures new, we will not forget the power we are finding - the power to redefine the rules. For this is how to use bitcoin and release the burden on the current system. It stands as a testament to the power of code that you can run an entity, without barriers, without red tape, without announcing your names or identity, where you create the rules.
And so we invite you to the Bitcoin Culture Festival at Tooting Market, The Dockside Vaults and Cyphermunk House, and an explosion of culture from the We Are 2140 collective. Together we will host a brand-new exhibition; the Culture of Code and stamp a sequence of blocks with so much creativity that no Londoner will miss it.
These are the signals of hope found in a civilisation mathematically backed by a money that extracts nothing from you. Embrace them. Support them - your fellow plebs and meetups. Network, connect and build. There is so much more to do and so much more to learn, but for now I've learnt this much - align your passions with bitcoin and every moment is a pill.
Onward plebs.
FIND OUT MORE
OUR PARTNERS / SPONSORS
-
 @ 8cb60e21:5f2deaea
2024-09-10 21:14:08
@ 8cb60e21:5f2deaea
2024-09-10 21:14:08 -
 @ 95a69326:6ac402e2
2024-10-24 20:09:01
@ 95a69326:6ac402e2
2024-10-24 20:09:01That is true for the rate of growth of addresses, of hashrate, and even of price.
None follow an exponential curve.
And that is fantastic news, because it’s a reality check on where we are today with Bitcoin adoption, and how to actually make it happen faster. Let us collectively break the culture that has formed around the S curve. The very idea that adoption is exponential.
It’s the hopium that keeps some going, waiting on the #OmegaCandle chanting NGU and hodling onto their Bitcoin like it’s their “precious”.
So much of Bitcoin’s narrative is centered around an imminent inflection point, a face-melting exponential curve. We will wake up one day (soon!), Bitcoin will be over 1m per coin, the Federal Reserve will be blown into pieces, and all Bitcoiners around the world will come together to sing Kumbaya.
Then one more year passes, then one more year passes, then one… Just one more! It’s around the corner guys! Just hold on to your Bitcoin, and everyone else can have fun staying poor.
Don’t get me wrong, Bitcoin is a marvellous savings technology. Once you see it, you understand it’s the best way to safeguard your financial future.
But this is not a game measured in weeks, or months. It’s a game measured in years, decades. And I am starting to believe that the reason so many Bitcoiners still have an unrealistic expectation of the short term adoption rate of Bitcoin, is exactly because so many still believe Bitcoin growth follows an exponential.
But that mentality is actually harming Bitcoin adoption. When you ground your belief system into an exponential, it also becomes very easy to believe the path is set. That you can sit back, and wait. That it’s “any day now”.
And you’re wrong! The path is not set, the path is still being written, and at the moment it’s being increasingly written by some suits at BlackRock. So extend your time horizon.
Stop believing hyper-Bitcoinisation is around the corner, and start asking yourself: what can I do to make Bitcoin adoption happen?
The truth is, if you want Bitcoin adoption, hodling Bitcoin won’t get you there. Spending it, and getting more people to use it will.
No, I’m not trying to psy-op you into selling your Bitcoin. And the idea that spreading Bitcoin promotes adoption is not just theory.
Let’s go over some data.
If you’re allergic to charts and data, maybe stop reading here, and ponder on the above question for a little while.
But if you’re not, take a look at this chart:
This is what it looks like when you chart the ratio of Bitcoin’s hashrate, price and number of addresses. Bitcoin is a beautiful combination of power laws.
We’re not making any predictions here. This is what is, and what has been since Bitcoin’s Genesis Block. It’s Bitcoin’s DNA. And what it tells us is that there is a known, quantifiable, symbiotic relationship between Bitcoin’s number of participants (\~addresses), Bitcoin’s security (hashrate) and Bitcoin’s price.
What else do we know?
Bitcoin’s address count (\~ participants) grows at a rate of x³, where x is time. That’s the growth rate of viruses, it’s the growth rate of social networks. Metcalfe’s Law says that the value of a network is approximatly equal to the square of its participants. And with Bitcoin that checks out. Bitcoin’s price grows at a rate of x⁶, which is x³ (participants) squared (again refer to Giovanni’s work for the in-depth data analysis).
That’s pretty solid data to say that:
Bitcoin’s price is not exponential The number of participants in the network has a quantifiable impact on its price So, Bitcoin growth follows a power law. And that’s fast! But compared to an exponential, that’s slooooow.
“But ETFs are here! NgU!! Scarcity!! Bitcoin will break all your models to the upside!!!”
It get’s tiring, and you know it.
Before you get all excited about ETFs buying up all the Bitcoin, leading to the mother of all supply squeezes and sending Bitcoin to the moon, realise this: the number of people owning Bitcoin has a bigger impact on price than supply and scarcity.
Sorry Stock2Flow fanatics, I’ll say that again. The number of people owning Bitcoin has a bigger impact on price than supply and scarcity.
And, to be fair, ETFs are bringing a lot of new network participants. But HODLING isn’t. And a lot of the Bitcoin that is going into the ETFs, is on a one way street to be hodled forever.
So going back to the big question: What can I do to accelerate Bitcoin adoption?
The answer is simple: get more people using Bitcoin.
Ok, that sounds obvious, and you already knew that. So this post was pointless.
But what is the pre-dominant narrative for getting more people to use Bitcoin today? It’s NgU, it’s scarcity, in other words, it’s all the wrong things. You won’t bring more network participants by buying up as much Bitcoin as you can to stash it away for the next 20 years.
Oh, and you won’t retire in 2 years for hodling that 0.1BTC either.
You’ll beat inflation, by a healthy margin, and you will get more purchasing power over time.
But the truth is, from Bitcoin’s adoption perspective, you’re a rent seeker.
You’re living off the work of those that are actually doing something to push Bitcoin’s adoption, ultimately having a real impact on its demand, and thus its price.
Who are they?
The educators teaching Bitcoin to new people. The meetup organisers bringing people together to talk about Bitcoin. * Those building circular economies. The protocol devs working on improvements to scale Bitcoin. The app devs working on making Bitcoin usable in every day life. The people spending Bitcoin on their everyday expenses. Those are the people pushing forward Bitcoin adoption.
Heck, even the wall street guy that orange pilled Larry Funk has done more for adoption than the perpetual holder waiting on the day he’ll be a citadel king.
I’ll end this rant here, and if there’s only one thing you remember from it let it be this:
Stop hodling Bitcoin to your death. Spend it, spread it, replace it. Support circular economies and Bitcoin educators, find local stores that accept it, get more people actually using the thing and you might just get to enjoy hyper-Bitcoinisation in your lifetime.
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
Bitcoin Power Law refs:
[Modelling Bitcoin Growth with Network Theory] https://bitposeidon.com/f/modeling-bitcoin-growth-with-network-theory…
[Intro to the Power Law] https://bitposeidon.com/f/simple-introduction-to-the-power-law-theory
-
 @ 655a7cf1:d0510794
2024-09-10 13:16:15
@ 655a7cf1:d0510794
2024-09-10 13:16:15Currently have kyc BTC, huge fan of lightning Network. Because I am a constant user of lightning. Plan on doing my business with lightning as well , peer-to-peer I'm not sure if I'm so worried about kyc I might be misguided in this situation.
originally posted at https://stacker.news/items/679520
-
 @ 83794dfe:e46c6636
2024-10-24 20:08:28
@ 83794dfe:e46c6636
2024-10-24 20:08:28i can post a note from my desktop to Nostr using Comet @captv
iuihuhjhjhjk
-
 @ 09fbf8f3:fa3d60f0
2024-09-10 13:12:15
@ 09fbf8f3:fa3d60f0
2024-09-10 13:12:15由于gmail在中国被防火墙拦截了,无法打开,不想错过邮件通知。
通过自建ntfy接受gmail邮件通知。 怎么自建ntfy,后面再写。
2024年08月13日更新:
修改不通过添加邮件标签来标记已经发送的通知,通过Google Sheets来记录已经发送的通知。
为了不让Google Sheets文档的内容很多,导致文件变大,用脚本自动清理一个星期以前的数据。
准备工具
- Ntfy服务
- Google Script
- Google Sheets
操作步骤
- 在Ntfy后台账号,设置访问令牌。
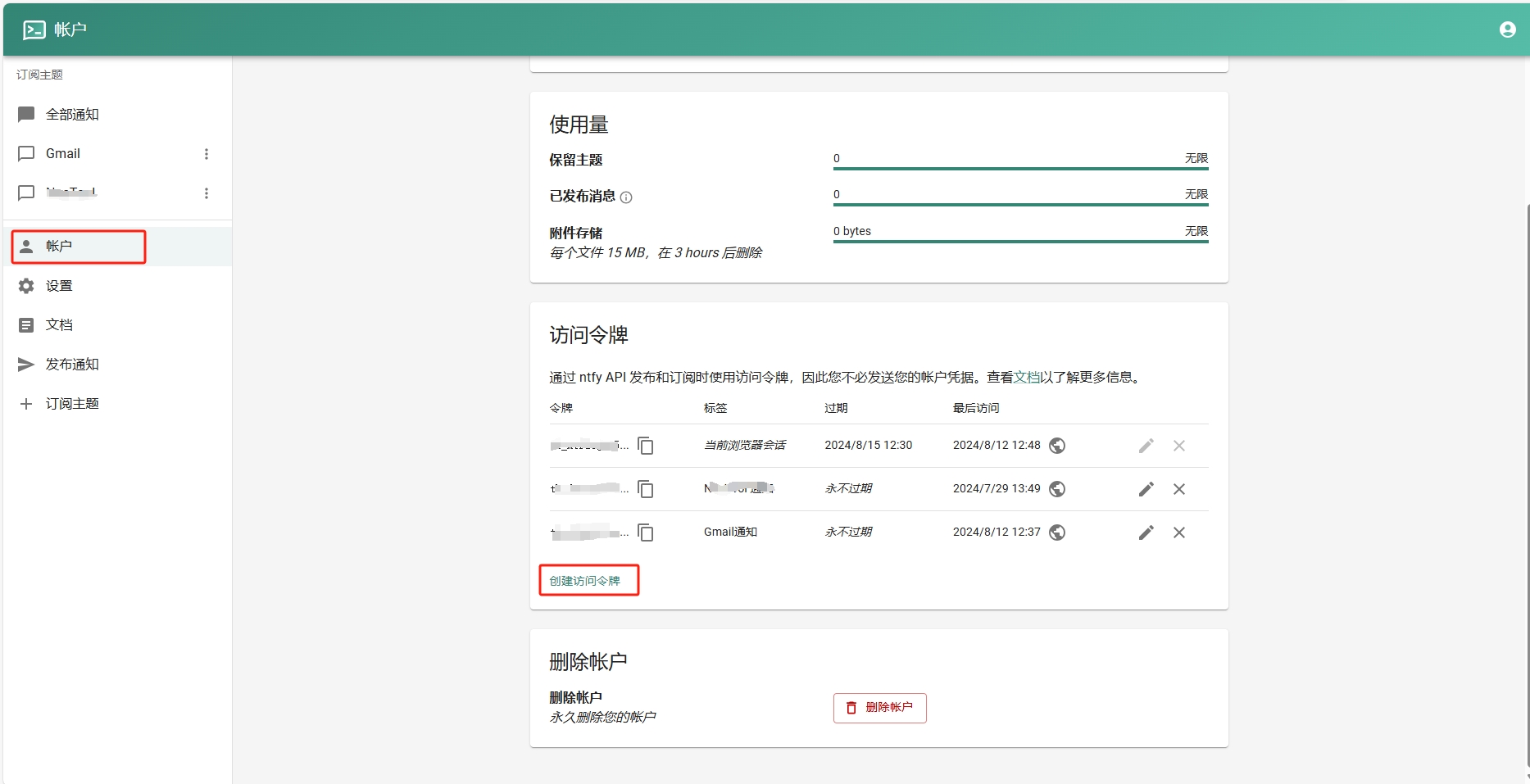
- 添加订阅主题。
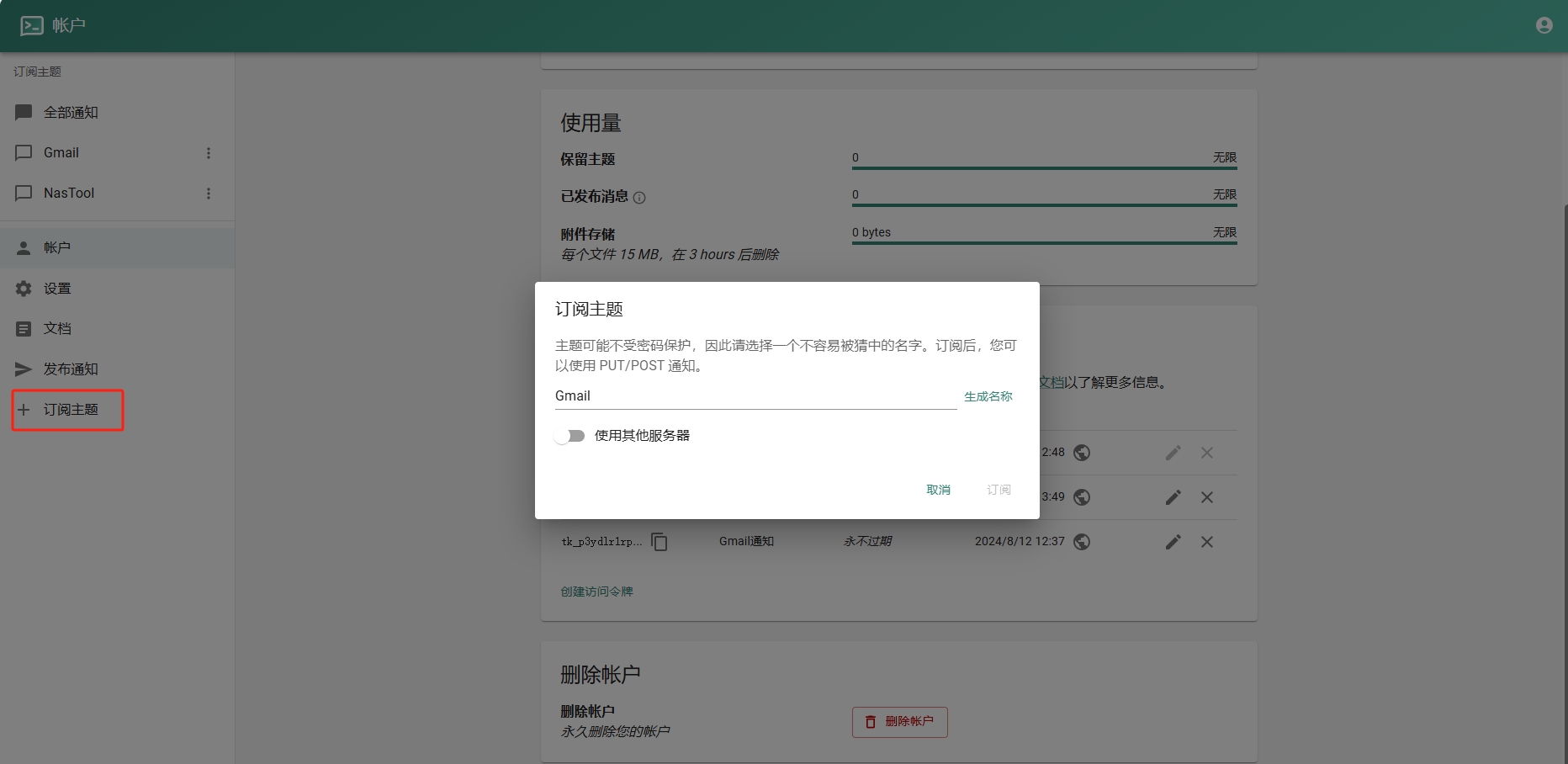
- 进入Google Sheets创建一个表格.记住id,如下图:
- 进入Google Script创建项目。填入以下代码(注意填入之前的ntfy地址和令牌):
```javascript function checkEmail() { var sheetId = "你的Google Sheets id"; // 替换为你的 Google Sheets ID var sheet = SpreadsheetApp.openById(sheetId).getActiveSheet();
// 清理一星期以前的数据 cleanOldData(sheet, 7 * 24 * 60); // 保留7天(即一周)内的数据
var sentEmails = getSentEmails(sheet);
var threads = GmailApp.search('is:unread'); Logger.log("Found threads: " + threads.length);
if (threads.length === 0) return;
threads.forEach(function(thread) { var threadId = thread.getId();
if (!sentEmails.includes(threadId)) { thread.getMessages().forEach(sendNtfyNotification); recordSentEmail(sheet, threadId); }}); }
function sendNtfyNotification(email) { if (!email) { Logger.log("Email object is undefined or null."); return; }
var message = `发件人: ${email.getFrom() || "未知发件人"} 主题: ${email.getSubject() || "无主题"}
内容: ${email.getPlainBody() || "无内容"}`;
var url = "https://你的ntfy地址/Gmail"; var options = { method: "post", payload: message, headers: { Authorization: "Bearer Ntfy的令牌" }, muteHttpExceptions: true };
try { var response = UrlFetchApp.fetch(url, options); Logger.log("Response: " + response.getContentText()); } catch (e) { Logger.log("Error: " + e.message); } }
function getSentEmails(sheet) { var data = sheet.getDataRange().getValues(); return data.map(row => row[0]); // Assuming email IDs are stored in the first column }
function recordSentEmail(sheet, threadId) { sheet.appendRow([threadId, new Date()]); }
function cleanOldData(sheet, minutes) { var now = new Date(); var thresholdDate = new Date(now.getTime() - minutes * 60 * 1000); // 获取X分钟前的时间
var data = sheet.getDataRange().getValues(); var rowsToDelete = [];
data.forEach(function(row, index) { var date = new Date(row[1]); // 假设日期保存在第二列 if (date < thresholdDate) { rowsToDelete.push(index + 1); // 存储要删除的行号 } });
// 逆序删除(从最后一行开始删除,以避免行号改变) rowsToDelete.reverse().forEach(function(row) { sheet.deleteRow(row); }); }
```
5.Google Script是有限制的不能频繁调用,可以设置五分钟调用一次。如图:
结尾
本人不会代码,以上代码都是通过chatgpt生成的。经过多次修改,刚开始会一直发送通知,后面修改后将已发送的通知放到一个“通知”的标签里。后续不会再次发送通知。
如需要发送通知后自动标记已读,可以把代码复制到chatgpt给你写。
-
 @ 0e501ec7:de5ef3a4
2024-10-24 20:03:28
@ 0e501ec7:de5ef3a4
2024-10-24 20:03:28Ik maak even een kleine sprong in de tijd, stichting Elzeard bespreek ik later nog ;)
Vandaag (24/10) vertrokken we bij Patsy en Els. Patsy is de meter van Tim, en hij heeft een kleine traditie om altijd bij hun langs te gaan als hij in de Ardennen fietst. Ze kochten ongeveer tien jaar geleden een wei in Marcourt, en besloten op een gegeven moment om daar te gaan wonen en een huis te bouwen. Ze hebben een bijna-passief woning, een leuke moestuin en veel fruitbomen, en op de wei staan er schapen van een zekere Eddy. Ze spreken aardig wat frans, en zijn zeer betrokken bij het sociale leven in het dorp! Niet zoals de tweede-verblijf-vlamingen die in grote getallen rust opzoeken in de Ardennen dus. We hielpen bij hun in de tuin, brandhout zagen en kappen, hooi leggen in de moestuin (ze doen geen bodembewerking! Voeren enkel hooi aan om de structuur te verbeteren en kruid tegen te werken). Daarnaast hielpen we ook met wat bomen en struiken te verplanten, en deed Tim zijn job als fietsenmaker. We aten verrukkelijk in de avond, van de heerlijke kookkunsten van Els. Een van de avonden (triggerwarning: vlees eten) was het een gerecht met vlees van een Lam, een van de diertjes die op de wei zelf geboren was en gegroeid. Tot het dus geslacht werd, en Patsy en Els er hun deeltje van kregen/kochten. Ik vond het wel een heftige ervaring om dat te eten, maar het voelde niet persé slecht. Denk ik. Al zag ik wel af en toe een Lammetje door een veld huppelen als ik met mijn ogen knipperde.
Het waren fijne dagen bij hun, maar het deed ook deugd om weer verder te gaan: gewoon op de fiets, en niet meer te hoeven socialiseren. In het begin van de dag moest ik nog even op gang komen, had wat pijn aan mijn rug van een forse beklimming zonder opgewarmd te zijn (het was ook een koude ochtend). Ook was Tim een paar keer een beetje fors (ms was het ook voor hem ochtend, kan zijn :) )waardoor ik mij even niet heel top voelde, moe en wat verdrietig, niet zo geborgen en energiek. Ik begon te twijfelen of ik wel sterk genoeg was voor deze reis, om met Tim mee te kunnen, om zonder veilige haven te zijn. Na een tijdje chieken en tobben, probeerde ik naar het landschap te kijken, en dat als veilige haven te zien. Niet zo heel makkelijk, geen vanzelfsprekende veilige haven, je moet eerst voorbij het landschap als decor, en het landschap als vluchtige voorbijgaandheid. Maar het hielp wel. De glooiingen van de Aarde, hun heuvels, de Bomen in de wind, de zachte Wolken met hun zwevende texturen, de verbaasde Koeien, het is ook wel thuis. Ik ben ook hier thuis. (Deze avond toen we begonnen te koken kwam een Reetje op bezoek, keek even heel doordringend en stoof rond ons weg. Dag Reetje; tot ziens.) Daarna overwon ik mijn obsakels en begon ik erover tegen Tim, niet gemakkelijk, maar was wel heel fijn, hij begreep het wel, luisterde wel. Zei ook dat hij zich al afvroeg of er iets was (zie je wel). Daarna voelte ik mij dus helemaal beter, en hadden we nog een zalige fietstocht. De zon kwam erdoor, het was warm, de heuvels gingen omhoog en omlaag, zoeffff. Ergens verloor ik mijn handschoenen, die had ik los op mijn bagage gelegd en was dan vertrokken. Dus: terug! Gelukkig lagen ze niet al te ver weg, ze waren pas bij een grote boebel van mijn bagage gekieperd. We fietsten uiteindelijk 67km, en stegen bijna 1000m. Echt wel de zwaarste tocht tot nu, maar fysiek voelde het al een pak minder lastig als in de eerste weken. Mischief ben ik dan toch (fysiek) sterk genoeg? We passeerden onderweg nog het meest cute (cuteste?) Bio-winkeltje ooit, een klein kamertje vol met verse groenten, waar we waterkers en eitjes en nog een brood voor morgenvroeg kochten. Nu liggen we hier in een bos naast Sovet, en gaan we morgen weer verder. Slaapwel!
-
 @ 6ad3e2a3:c90b7740
2024-09-10 09:26:37
@ 6ad3e2a3:c90b7740
2024-09-10 09:26:37While I love traveling and usually feel enriched by the experience, I dread and detest the process of going to the airport and getting on a plane. It’s not that I’m afraid of flying — though a plane crash would be one of the worst ways to die — but that the airlines and airports have made the experience as inefficient, dehumanizing and cumbersome as possible. While in the short-term these measures might have generated some extra revenue, cut costs or staved off encroachment from competitors, long-term it cannot be good for the service you offer to be so universally reviled. In the interest of improving their product — and the experience of millions of future passengers including me — here are some practical suggestions:
1. Separate passengers from their bags as early as possible.
The single stupidest airline policy is that checking a bag costs extra while carry-ons are free. What that does is incentivize everyone to drag their luggage through the airport and onto the plane. This has several negative consequences:
a) Even though most airlines have assigned seats, everyone lines up 10 or 20 minutes before the start of the already too long boarding process, frantically hoping to secure some scarce overhead space rather than relaxing in the terminal and boarding at their leisure before the door closes.
b) The process of people filing into the narrow plane aisle(s) with their bags and taking time to load them into the overheads stalls the entire boarding process. Not only do people stand in line at the boarding gate, but they stand in line in the jet bridge and again in the aisle(s). Whereas boarding with purses, laptops and other small, under-the-seat items might take 10 minutes or so, getting all the luggage in takes half an hour. If there are 150 people aboard, that’s 3,000 minutes (50 hours) of human life squandered on a useless and stressful activity. Multiply that by thousands of flights per day.
c) The process of deplaning is also slow because everyone has to get their bags out of the overhead. That’s another 15-minute process that should take five.
d) Everyone going through security with all their carry-ons slows down the security line significantly and makes people have to arrive at the airport earlier.
e) Because everyone has their bags, they have to lug them around the terminal while using the restroom, eating or shopping for something to read. Having a 20-pound weight on your shoulder only makes the experience that much more miserable.
The solution to this is for airlines to allow free checked bags and charge for carry-ons with the exception of parents traveling with young children.
To make the process of checking bags more efficient and less cumbersome there should be an immediate drop-off outside the airport. Like curb-side check-in, but automated, a giant conveyor belt of sorts where everyone drops their bag that will be sorted appropriately inside. This drop off area would have security keeping an eye on it, but it would be self-serve and connect at all entry points including curb-side, the parking garage, from the train, etc.
There would be no need for bag tags because people could have an airport-certified chip inserted into their luggage that syncs with the traveler’s boarding pass, i.e., the system reads the chip and directs the bag to the proper gate underground. (Maybe there would be a plastic bin at all the drop-off points you into which you put your bag so luggage of different shapes, sizes and materials could move smoothly and reliably on the conveyor belt to its destination.)
Security details would have to be worked out (maybe you’d have to scan your boarding pass or passport at the bag drop to open it), but as it stands, once you drop your bag off at the curb or the check-in area, it’s essentially the same process now, i.e, it has to be scanned internally before being placed on the plane.
2. Eliminate Security Lines
Going through security would be far easier without all the bags, but to expedite and improve it further, we should make two key changes, neither of which should be beyond our capacity to implement.
a) Instead of a single-file conveyor belt scanned by humans, make the conveyor belt wide enough for everyone to put their laptops, belts, etc. on simultaneously. This could easily be done by providing plastic bins (as they do now), but with individual numbers and keys on them, like you’d find in most locker rooms. You’d grab bin 45, for example, pull the key out, put your things in it, lock it, walk through the metal detector, retrieve your bin on the other side, unlock it, get your things, put the key back in it, and it gets returned for re-use.
Instead of a bored-out-of-his-mind human looking at each bag individually, there would be a large scanner that would look at all the bags simultaneously and flag anything suspicious.
b) Just as there’s no reason to send the bags through the scanner single-file, there’s no reason to send the people through that way, either. Instead, install room-wide metal detectors through which dozens of people could walk simultaneously. Any passengers that set it off would be digitally marked by the detector, directed back out, shed the offending item into a numbered bin and collect it on the other side.
Basically, you’d drop anything big off before you even set foot in the building, and you’d drop everything else into a security bin, walk through without waiting and collect it on the other side.
3. Make sure the gates are clean, have enough seats to accommodate the passengers of even the largest planes that come through, ample charging stations and reliable and free wi-fi.
Because you’re no longer forced to line up and hustle for overhead space, you’ll be spending more time sitting comfortably in the terminal.
4. Have clean, efficient public transportation from the center of each city directly to the airport. (Some cities already have this.) Not a train, a bus and a one-mile walk.
There are smaller things airports could do to make the process even better — and I’ll suggest some below — but these three would at least make it tolerable and humane. It would shave off roughly an hour per trip, spare people the burden of schlepping around with heavy bags, wading through slow-moving security lines (which add stress if you’re in danger of missing your flight), standing in the terminal, waiting in line after line to sit in a cramped and uncomfortable seat for 20-30 minutes before the plane even takes off and remaining stuck in that seat 15 minutes after the plane has made it to the gate while people one by one painstakingly get their bags out of the overhead bins. Moreover, people could get to the airport later without rushing, and if they were early, they could relax in the terminal or get work done.
Here are some other suggestions:
- With fewer people using the overhead bins, rip them out. There would be a few bins at designated spots (just like there are a few emergency exits), but the interior of the plane would feel more spacious and less claustrophobic. You also wouldn’t risk hitting your head when you stood up.
- Airplanes should have reasonably priced (ideally free) wi-fi and outlets in each row. There’s no way it costs anywhere near the $35 per flight, per person GoGo Inflight absurdly charges.
- Treat airports as public squares — invest in their design as well as their functionality. Incorporate outdoor spaces, green spaces. Attract decent restaurants, bars, cafes. People unencumbered by bags and not rushing to wait in line to board 40 minutes early will be more able to enjoy the environment and arriving travelers will immediately get a good impression and be put at ease.
- Do not advertise mileage rewards from credit cards or other sources unless those miles are actually redeemable at a reasonable rate and on routes and times someone would actually fly. As it stands those programs are borderline fraud — you can fly a middle seat one way from NY to LA for 30,000 miles at 6 am, but that’s not why I signed up for the credit card. If mileage plans are too costly, scrap them.
I can anticipate some objections to these ideas, and I’ll address each one in turn.
1. This would cost too much money.
My suggestions would require a significant initial investment, but it would be but a small piece of the infrastructure outlay that’s sorely needed — and on which our current president campaigned — and it would create jobs. Moreover, it would save travelers tens of millions of hours per year. At $15 per hour — it would pay for itself in short order. (And taxpayers’ squandered time and awful experiences are exactly what their tax dollars should go toward remediating.)
2. It’s too much of a security risk.
Airport security is incredibly flawed right now, as tests repeatedly show. You can get prohibited items through security easily already, and it’s likely the screening process is mostly “security theater,” i.e., just for show. But to the extent this is a serious concern, the newer system might actually improve security due to improved technology spurred by the infrastructure investment. Better detection could be designed into the new system, rather than relying on bored-out-of-their-mind humans to scan endlessly through people’s toiletries expecting to find nothing for hours and days on end.
Moreover, airport security has never actually been an issue in the US. Even on 9/11, the flimsy security worked well — the hijackers managed only boxcutters on the tragically ill-fated flights, not guns or bombs. In other words, that was a failure of government intelligence, not one of airline security even when no one took his shoes off or had to worry about how many ounces of liquid was in his shampoo bottle.
3. I like free carry-ons because it saves me from waiting at the baggage claim.
Great, then pay extra for that. When something you like individually causes collective harm, there needs to be a cost for it. That we have the opposite system where people doing what would make everyone else’s experience easier and better have to pay is perverse.
The bottom line — the current state of air travel both in the US and Europe is unacceptable*. We cannot have a system in which everyone participating despises it and simply pretend it’s an inevitable hassle about which we’re powerless to do anything. The central issue is the dehumanizing** lack of respect for travelers’ time and experience. It’s time to change our priorities and take care of the human beings for whom airports and air travel exist.
*I haven’t even touched on the awful state of flights themselves with cramped seats, small, dirty rest rooms, bad food and exorbitant fees to change your itinerary. That’s because I wanted to focus mostly on the airport/government side over which the public has ownership, and fixing the overall economics of air travel is probably more difficult than getting airlines to reverse their checked-bag fee policies.
** This article was written in March of 2017, and little did I know how much more dehumanizing things would get during covid.
-
 @ 6ad3e2a3:c90b7740
2024-09-10 08:21:48
@ 6ad3e2a3:c90b7740
2024-09-10 08:21:48I’ll write a separate Week 1 Observations later, but I wanted to dedicate this space solely to mourning my Circa Survivor entry.
Circa Survivor costs $1000 to enter and has a $10M prize for the winner, usually split by several as things get down to the wire. Three years ago, when the prize was $6M Dalton Del Don and I — the first time we ever entered — made it to the final 23 in Week 12. The value of our share was something like $260K at that point, but we got bounced by the Lions who beat the 12-point favored Cardinals and took home nothing.
When you enter a large survivor pool, the overwhelming likelihood is you’ll meet this fate at some point, whether in Week 1 or 12. So it’s not really the loss that’s painful, so much as not getting to live and die each week with a chosen team. You lose your status as “the man in the arena whose face is marred by dust and sweat and blood” and become just an observer watching and commentating on the games without the overarching purpose of surviving each week.
This year was also different due to the lengths to which I went to sign up. It’s not just the $1000 fee, it’s getting to Vegas in person, the $400 in proxy fees (you need locals to input your picks for you if you don’t live there), the $60 credit card fee, the $200 crappy hotel I booked at the last minute, the flights (one of which was cancelled due to heat), the rental car that necessitated, the gas, getting lost in the desert, the entire odyssey while sick and still jet-lagged in 122-degree heat.
But it’s not about the money, and it’s not even about the herculean effort per se, but the feeling and narrative I crafted around it. I was the guy who got this done. I flew from Portugal to San Francisco for 12 hours, two days later from SF to Palm Springs to help my 87-YO uncle with his affairs, improvised to get from Palm Springs to Vegas, which took six hours due to road closures, signed up for the contests, made the flight back to San Francisco, flew to Denver at 7 am the next day, took my daughter the Rockies game in the afternoon and then on to Boulder the following day. Maybe that’s not so impressive to some of you, but for me, an idle ideas person, a thinker, observer, someone who likes to express himself via a keyboard, it was like Alexander the Great conquering Persia.
And it’s not only about that smaller mission, or the narrative I crafted around it, but a larger one which was to bring sports content to nostr which I vowed to do before the summer which is why I felt I had to make the effort to get to Vegas to sign up for the contests, to have sufficient skin in the game, to have something real about which to write.
And I got the idea to do this seriously because Heather wrote a guide to Lisbon which I posted on nostr, and a few prominent developers there were surprisingly excited about getting that kind of quality content on the protocol. And I thought — if they’re this excited about a (very in-depth) guide to one particular city in Europe, how much more value could I create posting about a hobby shared by 50-odd million Americans? And that thought (and the fact I had to go to Palm Springs anyway) is what set me off on the mission in the first place and got me thinking this would be Team of Destiny, Part 2, only to discover, disappointingly, it’s real destiny was not to make it out of the first week.
. . .
While my overwhelming emotion is one of disappointment, there’s a small element of relief. Survivor is a form of self-inflicted torture that probably subtracts years from one’s life. Every time Rhamondre Stevenson broke the initial tackle yesterday was like someone tightening a vice around my internal organs. There was nothing I could do but watch, and I even thought about turning it off. At one point, I was so enraged, I had to calm down consciously and refuse to get further embittered by events going against me. Mike Gesicki had a TD catch overturned because he didn’t hold the ball to the ground, The next play Tanner Hudson fumbled while running unimpeded to the end zone. I kept posting, “Don’t tilt” after every negative play.
There’s a perverse enjoyment to getting enraged about what’s going on, out of your control, on a TV screen, but when you examine the experience, it really isn’t good or wholesome. I become like a spoiled child, ungrateful for everything, miserable and indignant at myriad injustices and wrongs I’m powerless to prevent.
At one point Sasha came in to tell me she had downloaded some random game from the app store on her Raspberry Pi computer. I had no interest in this as I was living and dying with every play, but I had forced myself to calm down so much already, I actually went into her room to check it out, not a trace of annoyance in my voice or demeanor.
I don’t think she cared about the game, or about showing it to me, but had stayed with her friends most of the weekend and was just using it as an excuse to spend a moment together with her dad. I scratched her back for a couple seconds while standing behind her desk chair. The game was still going on, and even though I was probably going to lose, and I was still sick about it, I was glad to have diverted a moment’s attention from it to Sasha.
. . .
In last week’s Survivor post, I wrote:
What method do I propose to see into the future? Only my imagination. I’m going to spend a lot of time imagining what might happen, turn my brain into a quantum device, break space-time and come to the right answers. Easier said than done, but I’m committed.
It’s possible I did this, but simply retrieved my information from the wrong branch of the multiverse. It happens.
. . .
I picked the Bengals knowing full well the Bills were the correct “pot odds” play which is my usual method. Maybe when the pot-odds are close, I might go with my gut, but they were not especially close this week, and yet I still stuck with Cincinnati because they were the team I trusted more.
And despite it being a bad pick — there are no excuses in Survivor, no matter what happens in the game, if you win it’s good, and lose it’s bad — I don’t feel that badly about it.
I regret it only because I wish I were still alive, but it was my error. I went with what I believed, and it was wrong. That I can live with 100 times better than swapping out my belief for someone else’s and losing. Had I done that I’d be inconsolable.
. . .
I won’t let the Survivor debacle undermine my real mission to bring sports to nostr. Team of Destiny 2 would have been a compelling story, but it was never essential. After all, my flight was cancelled and I had to improvise, so now my Survivor entry is cancelled, and I’ll have to improvise again. The branch of the multiverse where the Bengals won didn’t give me the information I wanted, but maybe it was what I really needed to know. That I am the man in the arena yet, the battle was ever against myself, and for a brief moment, while my team was losing, I prevailed.
-
 @ 83794dfe:e46c6636
2024-10-24 20:01:44
@ 83794dfe:e46c6636
2024-10-24 20:01:44i can post a note from my desktop to Nostr using Comet @captv
-
 @ a367f9eb:0633efea
2024-10-24 19:46:10
@ a367f9eb:0633efea
2024-10-24 19:46:10In the corridors of power in board rooms, lecture halls, and legislative chambers, Bitcoin is no longer an enigma resigned to just technology or economics enthusiasts.
After a decade of gradual adoption, Bitcoin is an innovation invoked in political debates, presidential speeches, quarterly earnings reports, and is now the most recognized “crypto” by anyone with an Internet connection.
And as adoption has grown, the ecosystem has grown with it, sprouting all kinds of various exchanges, hardware signing devices, applications, and much more. Even betting on political outcomes is now enabled by Bitcoin.
With more liquidity pouring into the protocol and people using Bitcoin as an investment or as a currency to buy and sell things, it is inevitable that rules and regulations will be introduced to set the rules of the game and to try to protect consumers.
The rules of the game
From the federal government down to state and sometimes municipal jurisdictions, there are now plenty of laws on the books that give direction to citizens on how their bitcoin is taxed, what rules exchanges must follow, and whether you can mine it in a certain area.
Think money transmission licenses, capital gains taxes, environmental permits, accounting standards, and regulatory guidance to institutions. With more yet to come, it is prudent for those of us in policy and business to advocate for the best policies that will empower bitcoin holders and entrepreneurs while ensuring a base layer of protection. We should also make the case for why Bitcoin is different and shouldn’t be pigeon-holed to just yet another financial product.
While many new legislative efforts are gaining steam in the House of Representatives in Washington or in state capitals, both positive and negative, we should never lose sight of one of the most unique qualities of Bitcoin that sets it apart from any other technology or money in the world: self-custody.
With Bitcoin, individuals have the ability to sovereignly hold their money without counterparties and censorship risk. By holding one’s own keys, simplified in 12 or 24-word seed phrases, people can claim ownership over their small unlocked portion of the Bitcoin blockchain at the total exclusion of anyone else. This is one of Satoshi’s most brilliant gifts in the code.
As digital cash, bitcoin cannot be unilaterally usurped or confiscated from a bank account. Its value is the representation of a true free market set by buyers and sellers, and those who own the keys are the only ones who can move the units from one address to another.
There is always the risk of physical theft, either by so-called 5 dollar wrench attacks or seed phrase compromise, but the point remains that the ownership model of Bitcoin makes it unique. As long as a holder is using their own keys to move or safeguard their bitcoin, we should also be clear that any legislative proposal that aims to restrict the movement or possession of bitcoin is beyond the pale.
Self-custody as the prime directive
As policy advocates who seek to influence smart, defensive rules on Bitcoin, that means that our prime directive must be protecting, defending, and demarcating self-custody from other custodial solutions that may exist in the market. Self-custody, as a practice, an innovation, or a method of possession, is nonnegotiable.
We know there will be stringent regulations on institutions holding bitcoin on behalf of their customers or products that custody bitcoin, and that is fine and likely necessary. There are well-founded concerns that jurisdictions should protect users from risk if their assets are stored outside of their control.
We can submit that there will be reasonable rules on the various interactions between fiat money from the traditional system and Bitcoin. The on and off ramps will always be the places for regulatory scrutiny, as will concerns about sanctions lists and illicit activities. So will ensuring that no one is committing fraud or deception, or as in the case of FTX and other exchanges, discretely re-allocating customer assets for risky bets.
But once these rules begin to restrict the activities of users with bitcoin in self-custody, who send funds to other wallets and users who also maintain self-custody, there must be an effective line in the sand. This also applies to protocols and software that allow users to perform collaborative transactions, or to privately send between addresses, as in the case of the developers of Samourai Wallet and similar services (be sure to check out P2P Rights).
Previous attempts at flagging or IDing “self-hosted” wallets that receive amounts over a certain threshold were initially found in the European Union’s cryptocurrency regulations, but those were thankfully scuttled. But we must remain vigilant that no similar proposal aims to do the same in our own country.
Regardless of how Bitcoin grows, we must articulate the case for self-custody to be clear and distinctly separate from custodial solutions, as my colleague and BPI Legal Fellow Zack Shapiro has eloquently covered. Shoehorning noncustodial products into legislation or rules meant for custody relationships would be overburdensome, unnecessary, and essentially erase the entire point of Bitcoin in the first place.
The right to self-custody shall not be infringed.
Originally published at the Bitcoin Policy Institute.
-
 @ 3589ce32:ef4269ad
2024-10-24 19:13:56
@ 3589ce32:ef4269ad
2024-10-24 19:13:56Bitcoin y la Descentralización:
Bitcoin se centra en la soberanía individual, la libertad financiera y la descentralización. Su filosofía se basa en la confianza en un sistema sin intermediarios, donde cada individuo tiene control sobre sus recursos. La descentralización de Bitcoin refleja un despertar hacia la autonomía personal, la autosuficiencia y la búsqueda de la verdad fuera de estructuras de poder tradicionales.
UCDM enseña la no-dualidad, el perdón y la percepción correcta, destacando que el amor es lo único real y que todo lo demás es una ilusión. La idea es la de liberarse de la mentalidad de escasez (tan presente en el dinero tradicional) y fomentar una mentalidad de abundancia, confianza y cooperación.
El Vedanta Advaita es una filosofía no dualista que enseña que solo hay una realidad última, y que todo es una manifestación de esa unidad. La dualidad es una ilusión. Guardando ciertas distancia, podríamos decir que la unidad subyacente del Advaita se refleja en la idea de una red descentralizada y sin fronteras, como Bitcoin, la cual conecta a las personas sin intermediarios. También ¿Cómo superar la ilusión del ego y la dualidad para alcanzar una verdadera libertad? Hablaremos de esto en otra ocasión …
-
 @ 862fda7e:02a8268b
2024-09-10 01:32:05
@ 862fda7e:02a8268b
2024-09-10 01:32:05I have a lot of dreams where I'm playing a claw machine and just winning a ton of toys. One of the best clawe machine dreams is where I come across claw machines with large toys as prizes, it had carnival toys from the 70's-80's as prizes. Unfortunately, the claw machine was non functional as it was pretty old. In most of these dreams I am winning an endless amount of toys, so much so that the prize chute becomes full with toys. In real life, they rig claw machines. Often times, the owners of the machines set it so they must meet a certain "pay out" before the claw will actually grip a prize. So while you might have a great aim on getting the claw around a toy, it won't grip it firmly enough until enough money has been inserted to meet that payout. Some claw machines will do a fake out, where it will grab the prize, then once the claw gets back to the top of the machine, it will drop the prize. It's to trick you that it got it, but it actually didn't. Sadly, claw machines are worthless to play these days. It's become highly monetizable and impossible to win. I'm great at claw machines, but it's just a matter of luck with hitting the payout these days.
-
 @ 129f5189:3a441803
2024-09-09 23:28:41
@ 129f5189:3a441803
2024-09-09 23:28:41Project 2025, outlined in the Heritage Foundation's "Mandate for Leadership" document, serves as a fundamental guide for the next Republican administration. Despite Trump's extensive denial, in today's material, we will explore the deepening and continuation of many policies already employed during his first term. The idea is that this material will serve as a reference document to consult and verify what was actually implemented and/or followed. https://image.nostr.build/e3b89d71ff929258e5d9cb0b5ca8709a381598f43d8be4b17df3c69c0bc74d4a.jpg This document presents proposals for the foreign policy and the State Department of the United States of America, as well as the strategy with its political partners and adversaries. We will also address the U.S. government's communication strategy abroad. https://image.nostr.build/a4250b786f611b478aaf0be559427ad7d4296fbcacb2acc692c7f0d7eb06b0dd.jpg Reorienting U.S. Foreign Policy: Proposals for a Conservative Future In the chapter "The Department of State" from the "Mandate for Leadership," also known as "Project 2025," Kiron K. Skinner presents a comprehensive plan to reform U.S. foreign policy under a conservative administration. Skinner, a renowned foreign policy expert and former Director of Policy Planning at the U.S. State Department, outlines global threats and offers specific recommendations to strengthen the U.S. position on the international stage. Below, we present a detailed analysis of the proposals, emphasizing direct quotes and explanations of the key points discussed. https://image.nostr.build/278dcd7ef0439813ea35d0598319ee347f7a8cd7dfecac93be24ffdd0f6ecd04.jpg History and Structure of the State Department Since its founding in 1789, the State Department has been the primary diplomatic channel of the U.S. With nearly 80,000 employees and 275 posts around the world, it faces significant structural challenges. Skinner highlights that "the biggest problem of the State Department is not a lack of resources," but the belief that it is "an independent institution that knows what is best for the U.S." (Skinner). The scholar and former Director of Policy Planning at the U.S. State Department during the Trump administration emphasizes these points, considering the difficulty in accepting a conservative international approach by State Department employees (the equivalent of the Ministry of Foreign Affairs in other countries). https://image.nostr.build/049939926793e86000b300b9a962dc0ae7e271d9a607ae36d8cb08642adf4174.jpg Political Leadership and Bureaucratic Support To align the State Department with presidential priorities, Kiron suggests appointing political leaders who are committed to the president's vision. "Leadership should include political appointees in positions that do not require Senate confirmation, including senior advisors and deputy secretaries" (Skinner). Furthermore, she emphasizes the importance of training and supporting these appointees to ensure effective coordination between agencies. https://image.nostr.build/6ed704cc9612aa6489e048b143f1e489c1f8807fdf2ab011b4ba88e4a1e3619a.jpg Global Threats to the U.S. The document identifies five countries that pose significant threats to the security and prosperity of the U.S.: China, Iran, Venezuela, Russia, and North Korea. 🇨🇳 China: Skinner argues that China represents an existential threat. "The U.S. needs a strategic cost-imposing response to make Beijing's aggression economically unviable" (Skinner). Additionally, she emphasizes that the issue is not with the Chinese people, but with the communist dictatorship that oppresses them: "As with all global struggles against communist and other tyrannical regimes, the issue should never be with the Chinese people, but with the communist dictatorship that oppresses them" (Skinner). https://image.nostr.build/e707273f1d08bdc4187123a312bd116695b5f603066e11ad30fcef4466730b6b.jpg 🇮🇷 Iran: The Obama administration, through the 2015 nuclear deal, provided the Iranian regime with a "crucial cash bailout" (Skinner). Kiron criticizes this approach, asserting that the U.S. should support the Iranian people in their demands for a democratic government. "The correct policy for Iran is one that recognizes that it is in the U.S. national security interests and the human rights of Iranians that they have the democratic government they demand" (Skinner). https://image.nostr.build/cda7d29a62981f59ad8d77362b3867b552f190c8d7e0e8d9233cb7c1d1d0309e.jpg 🇻🇪 Venezuela: Under the regimes of Hugo Chávez and Nicolás Maduro, Venezuela has transitioned from a prosperous country to one of the poorest in South America. Skinner suggests that the U.S. should work to contain Venezuelan communism and support its people. "The next administration should take steps to put Venezuela's communist abusers on notice and make progress in helping the Venezuelan people" (Skinner). https://image.nostr.build/f53e12564cae74d4b50c24b0f3752dd2c53b70bd1c00a16df20736fb8588417d.jpg 🇷🇺 Russia: The war between Russia and Ukraine divides opinions among conservatives, and the document considers three lines of action. Some advocate continuing support for Ukraine, while others believe that such support does not serve U.S. security interests. "The conservative approach rejects both isolationism and interventionism, first asking: What is in the interest of the American people?" https://image.nostr.build/8fedaf77129f4801f4edb8b169b2ac93a3e518b8bf3642b3abc62575b5435fa3.jpg One conservative school of thought believes that "Moscow's illegal war of aggression against Ukraine represents major challenges to U.S. interests, as well as to peace, stability, and the post-Cold War security order in Europe" (Skinner). This view advocates for continued U.S. involvement, including military and economic aid, to defeat Russian President Vladimir Putin and return to pre-invasion border lines. Another conservative school of thought argues that U.S. support for Ukraine is not in the interest of U.S. national security. According to this view, "Ukraine is not a member of the NATO alliance and is one of the most corrupt countries in the region" (Skinner). It is argued that the European nations directly affected by the conflict should help defend Ukraine, but the U.S. should seek a swift end to the conflict through a negotiated settlement. https://image.nostr.build/22db3d0e79340c1d62344a2b8a3bfddbe4d5bd923cf77d70cfbf5ebf73e4db3e.jpg A third conservative viewpoint avoids both isolationism and interventionism, proposing that "each foreign policy decision should first ask: What is in the interest of the American people?" (Skinner). From this perspective, continued U.S. involvement should be fully funded, limited to military aid while European allies address Ukraine's economic needs, and must have a clear national security strategy that does not endanger American lives. https://image.nostr.build/939fea0bb5c69f171a3da1073e197edcff23a600430b3bc455f6d41bc8a0319f.jpg Although not stated explicitly, I believe this third viewpoint is the one Kiron Skinner desires, as she considers American intervention important but advocates for balancing the costs of the war with its partners in the European Union and NATO. https://image.nostr.build/d1d0c7fb27bfc5dd14b8dde459b98ed6b7ca2706473b2580e0fbf5383f5a9c10.jpg 🇰🇵 North Korea: North Korea must be deterred from any military conflict and cannot be allowed to remain a de facto nuclear power. "The U.S. cannot allow North Korea to remain a de facto nuclear power with the capability to threaten the U.S. or its allies" (Skinner). https://image.nostr.build/95febb04f6d2e0575974a5e645fc7b5ec3b826b8828237ccc1f49b11d11d6bce.jpg Detailed Policy Proposals Refugee Admissions: The Biden administration has caused a collapse in border security and internal immigration enforcement, according to Skinner. She argues that the U.S. Refugee Admissions Program (USRAP) should be resized. "The federal government should redirect screening and verification resources to the border crisis, indefinitely reducing the number of USRAP refugee admissions until the crisis can be contained" (Skinner). https://image.nostr.build/a5740b33842e47b9a1ab58c7b72bd6514f9b6ffbb18706deed1445c59236bc0d.jpg Corporate Collaboration with China: Skinner criticizes the collaboration of companies like BlackRock and Disney with the Chinese regime, noting that "many are invested in an unwavering faith in the international system and global norms," refusing to acknowledge Beijing's malign activities. She emphasizes that the real issue is the communist dictatorship that oppresses the Chinese people, not the Chinese citizens themselves (Skinner). https://image.nostr.build/05a3c787f144c4519c2ee8a4b22e64b8729842819ace4b439c849ef70ecd60b4.jpg Fentanyl and Mexico: The trafficking of fentanyl, facilitated by Mexican cartels in collaboration with Chinese precursor chemical manufacturers, is a critical problem. "Mexican cartels, working closely with Chinese manufacturers of fentanyl precursor chemicals, are sending this drug to the U.S., causing an unprecedented lethal impact" (Skinner). The next administration should adopt a firm stance to halt this public health crisis. https://image.nostr.build/59e32aeef5dabab3344a94a3e415d57fed91fece8bc3c5f068e9f6f7d71f99bd.jpg Re-hemispherization of Manufacturing: Kiron proposes that the U.S. promote the relocation of manufacturing to partner countries such as Mexico and Canada. "The U.S. should do everything possible to shift global manufacturing to Central and South American countries, especially to move it away from China" (Skinner). This would improve the supply chain and represent a significant economic boost for the region. https://image.nostr.build/5d5d7d792f1c94eb6e2bd7a4b86c43236765719e183be8ba8e00ed7dd07eca66.jpg Abraham Accords and a New “Quad”: Skinner suggests that the next administration should expand the Abraham Accords to include countries like Saudi Arabia and form a new security pact in the Middle East that includes Israel, Egypt, Gulf states, and possibly India. "Protecting the freedom of navigation in the Gulf and the Red Sea/Suez Canal is vital for the global economy and, therefore, for U.S. prosperity" (Skinner). https://image.nostr.build/c87cd99cb3ea2bef40e9d1f1fea48b0c9f9f031f3077fff658f15f850e7b8589.jpg Policy for Africa: The U.S. strategy for Africa should shift focus from humanitarian assistance to economic growth and countering China’s malign activities. "Development assistance should focus on fostering free market systems and involving the U.S. private sector" (Skinner). She also highlights that African nations are opposed to the imposition of policies such as abortion and LGBT lobbying. https://image.nostr.build/44df42f32e61c14786ac46c231d368b14df4dc18124a0da458e8506f917302f2.jpg Relations with Europe and Asia Europe: The U.S. should demand that NATO countries increase their contributions to defense. "The U.S. cannot be expected to provide a defense umbrella for countries that do not contribute adequately" (Skinner). Additionally, urgent trade agreements should be pursued with the post-Brexit United Kingdom. https://image.nostr.build/6c013bacfa9e6505ad717104d9a6065f27664a321dd2c3d41fd7635258042d2f.jpg Asia: The withdrawal of U.S. troops from Afghanistan was humiliating and created new challenges. Skinner emphasizes the importance of India as a critical partner to counterbalance the Chinese threat and promote a free and open Indo-Pacific. Cooperation within the Quad, which includes the U.S., India, Japan, and Australia, is essential to this strategy. "The priority is to advance U.S.-India cooperation as a pillar of the Quad" (Skinner). https://image.nostr.build/1cc988b2f70d855c9676d7e38ffdb23564d04ad6333a8d256698f416a1c6704e.jpg International Organizations Skinner criticizes the corruption and failure of the World Health Organization (WHO) during the Covid-19 pandemic. "The next administration should end blind support for international organizations and direct the Secretary of State to initiate a cost-benefit analysis of U.S. participation in all international organizations" (Skinner). She also supports the “Geneva Consensus Declaration on Women’s Health and Protection of the Family,” which is against abortion, and believes that the U.S. government should not fund international organizations that promote abortion (Skinner). https://image.nostr.build/0b583511fef16d68736804fae2f15850eb5c803af01f006a3fe10cdbc583f48c.jpg Conclusion Skinner’s document provides a detailed vision for reorienting U.S. foreign policy under a conservative administration, with an emphasis on ensuring that the State Department serves the national interests defined by the president. With these guidelines, the next administration has the opportunity to redefine the U.S. position on the global stage, promoting security, prosperity, and freedom. https://image.nostr.build/697522745c5947cd4384cdd302b531ee98ce5d59a5d72de0b4f3a52c9abd4821.jpg
-
 @ e968e50b:db2a803a
2024-10-24 17:53:49
@ e968e50b:db2a803a
2024-10-24 17:53:49https://whosaidit.vercel.app/
I made a quiz for you. Let me know if you have any feedback. Please don't share your results or any spoilers here. I've already had some...uh...let's call if fun...sharing with friends and family. Much to @DarthCoin and many other stackers' chagrin, the purpose of this is not to convince people not to vote, although that may be the affect for some. I'm just trying to challenge people's thinking.
Also, it would be really easy for me to change any of the content. Let me know if you have feedback. I want to make this as effective and accurate as possible.
https://whosaidit.vercel.app/
originally posted at https://stacker.news/items/738766
-
 @ 129f5189:3a441803
2024-09-09 23:23:45
@ 129f5189:3a441803
2024-09-09 23:23:45Project 2025, outlined in the "Mandate for Leadership" document by the Heritage Foundation, is a crucial guide for the next Republican administration. Crafted by conservative intellectuals from major American think tanks, this plan promises to have significant influence on a potential Donald Trump administration, even if he does not formally acknowledge it as his government plan. https://image.nostr.build/443d69c16dc32659be2353ce48d170d397e0ee682ffc3c4108df3047fd54472d.jpg This document presents proposals to depoliticize government agencies, increase efficiency, and reduce costs, aiming to dismantle the Deep State and combat the Woke agenda associated with the Democratic Party. https://image.nostr.build/06de3f0de3d48e086f47d0418d30e32cbfe0d88f452a93706987b7394458952d.jpg Dissolution of the DHS and Redistribution of Functions The Department of Homeland Security (DHS) was established in 2002 in response to the September 11 attacks, with the goal of consolidating various agencies responsible for domestic security under a single command. The DHS includes agencies such as FEMA, TSA, ICE, and CISA. Project 2025's proposal to dissolve the DHS and redistribute its functions to other agencies aims to address excessive bureaucracy and a lack of cohesion, arguing that centralization has failed to effectively integrate its diverse missions. https://image.nostr.build/ffca8d274914b725183b8fb19162c1b63f4d987c24e598f2eca88901d4a1a43c.jpg Impact on the Democratic Deep State: The dissolution of the DHS would pose a significant threat to the Democratic Deep State, as it would redistribute the power concentrated in a single entity across multiple other agencies, making it more difficult to politicize and centralize control over domestic security operations. This decentralization would reduce the ability to use the DHS as a political tool against opponents. https://image.nostr.build/1597e3b88572fe8aae7ce67cdaf975a873cf8bc68f76d59cb4253ad1520fc7bc.jpg Primary Recommendations Combining Immigration Agencies: Merge U.S. Customs and Border Protection (CBP), Immigration and Customs Enforcement (ICE), U.S. Citizenship and Immigration Services (USCIS), the Office of Refugee Resettlement (ORR) of the Department of Health and Human Services (HHS), and the Executive Office for Immigration Review (EOIR) of the Department of Justice (DOJ) into a new autonomous border and immigration agency. https://image.nostr.build/58eef4f2eca0ed2400261ec878c1dba2ca4bca519a16751b1fb7abd45da2906b.jpg Privatization of the TSA: Privatize the Transportation Security Administration (TSA), drawing inspiration from Canadian and European models, to reduce costs and improve service for travelers. Division of the Secret Service (USSS): The U.S. Secret Service (USSS), responsible for protecting national leaders and investigating financial crimes, would be divided. The protective element would be transferred to the Department of Justice (DOJ), while the financial investigations element would be moved to the Department of the Treasury. https://image.nostr.build/0a065cdbf158db4bc17b9aacd4af5a94029004caaa152eebf2c557042b08a641.jpg Impact on the Democratic Deep State: The division of the USSS would significantly weaken centralized control over protection and financial investigations, making it more difficult to use these functions for political purposes. Transferring the protective element to the DOJ and the financial investigations element to the Treasury would complicate efforts for any group or party to manipulate these crucial government functions for partisan objectives. https://image.nostr.build/1597e3b88572fe8aae7ce67cdaf975a873cf8bc68f76d59cb4253ad1520fc7bc.jpg Cybersecurity and Infrastructure Security Agency (CISA) Established in 2018, CISA is a federal agency responsible for protecting the U.S. critical infrastructure from cyber threats. CISA's mandate includes ensuring cybersecurity for sectors such as energy, transportation, and healthcare, and it collaborates with public and private entities to strengthen the country’s cyber resilience. Criticisms and Restructuring Proposals: Project 2025 strongly criticizes CISA for deviating from its original mission and being used as a political tool for censoring speech and influencing elections. The proposal is to transfer CISA to the Department of Transportation (DOT) and return the agency to its statutory focus. https://image.nostr.build/8bfb4a45053de96a775f67e3e1b83a44d9a65fee4705e3b16d3359bd799b8af2.jpg Review of Executive Order 12333 Executive Order 12333, issued in 1981, sets guidelines for U.S. intelligence activities, including the collection, analysis, and dissemination of information. Project 2025 proposes a review of this order to ensure that intelligence agencies are not used for political purposes but are focused on protecting national security. Objectives of the Review: Prevent Abuse: Ensure that intelligence collection is conducted legally, without being used to target political opponents. Ensure Impartiality: Reaffirm that intelligence operations must be conducted impartially, with a sole focus on the country's security. https://image.nostr.build/90d31cb35a33048d311716df2fbc65c97bd4c1972977e266133654404393fca0.jpg Reforms in Public Service Facilitation of Public Employee Dismissal: Project 2025 emphasizes the need to simplify the process for dismissing public employees who do not perform their duties impartially or who promote specific political agendas. Performance Evaluations: The document highlights the importance of merit-based compensation, stating that performance evaluations are only effective when tied to real consequences. Research indicates that 90% of major private companies in the U.S. use a merit-based pay system linked to evaluations. However, in the federal government, compensation remains largely based on seniority, despite efforts to adopt merit-based pay. https://image.nostr.build/1b858fd7b2a23c3c65c0677d3e69c44976721bbdcbe7facf4682ba3371562cff.jpg Inclusion of Employees Aligned with Conservative Values: Aligned Hiring: Establish mechanisms to hire public employees who share conservative values, ensuring that the policies and practices of agencies are consistent with the principles endorsed by the administration. https://image.nostr.build/ddbf5c59e7bb479998433991347f9d301dd117fbca0edb0f94e98fcac90b2974.jpg Controversial Cases and Politicization: Hunter Biden Laptop Case: Project 2025 harshly criticizes the FBI and the Department of Justice, accusing them of acting in a biased and politically motivated manner. The authors suggest that the agency is intimidating parents who protest by labeling them as "domestic terrorists," while simultaneously suppressing politically unfavorable speech under the guise of combating "disinformation." Furthermore, the critique highlights that the FBI is alleged to be neglecting violent attacks on pregnancy centers and violations of laws prohibiting attempts to intimidate Supreme Court justices. The criticism intensifies with allegations that the FBI interfered in domestic elections and engaged in propaganda operations, specifically citing the purported Russian collusion conspiracy in 2016 and the suppression of the Hunter Biden laptop case in 2020, which is seen as a threat to the Republic. https://image.nostr.build/e4f571a14102a939164465498bef514379ec0443e71a58e12f50c518e00570c6.jpg Politicization of the FBI: Election Interference: Russia Hoax and Trump, Suppression of Hunter Biden’s Laptop, and Big Tech Collusion. Revelations about the FBI’s role in the 2016 "Russia Hoax" and the suppression of Hunter Biden’s laptop in 2020 suggest that the agency may have strayed from its impartial duties. These actions indicate concerning politicization, where the agency appears to have been used to influence the political landscape in favor of certain interests. This includes collaboration between the FBI and Big Tech companies to control discourse. https://image.nostr.build/5dcd45fcec939b782d29d8d2e3d3b45244c525b5dbd3240f1629a4632e390a86.jpg Comprehensive Review of FBI Investigations: It is crucial to conduct an immediate and thorough review of all significant investigations and activities within the FBI, terminating those that are illegal or contrary to national interests. This step is essential for restoring public trust in the FBI. A public report on the findings of this review could enhance transparency and confidence. https://image.nostr.build/df98e2c6aff123d806187eab13d24a3ebb30a87df1f44cf57be97dc5624fff88.jpg Structural Reorganization: Align the FBI within the Department of Justice (DOJ) according to its purposes of national security and law enforcement. The agency should be under the supervision of the Assistant Attorney General for the Criminal Division and the National Security Division, ensuring that the FBI does not operate as an independent entity but is instead subordinated to the DOJ’s directives. https://image.nostr.build/0d1c0015c6b67a8afc2dd1595357ea571fcd5a9d83829065f49f9b60cf553eb0.jpg Prohibition on Policing Speech: Prohibit the FBI from engaging in activities related to combating "disinformation" or "misinformation" disseminated by Americans who are not linked to plausible criminal activities. The Constitution, through the First Amendment, prohibits the government from policing speech, ensuring a healthy public debate without governmental intervention. All these measures represent a significant attack on the "Deep State" within American institutions. These public policies have been considered a dictatorial threat by many sectors of the American press. However, the real issue should be the politicization of unelected bureaucrats by a political faction. https://image.nostr.build/9a44b19d15d53314f89528c1d89e2f637030ea18d8907a6a8c4e27d07064b8ec.jpg Combating Woke Culture in the Intelligence Community Future leadership of the Intelligence Community (IC) needs to implement a plan to replace the "woke" culture and identity politics that have spread throughout the federal government. The goal is to restore traditional American values such as patriotism, racial impartiality, and job competence, which have been replaced by advocacy for "social justice" and identity politics. https://image.nostr.build/7929dca5e36273c8e751f36d6ca6229f362e30792bce735f10be7e5d8581af5f.jpg Final Considerations The Heritage Foundation’s Project 2025 is not merely an administrative reform plan; it is a manifesto of resistance against the Washington status quo. The proposals aim to dismantle established power structures, eliminate politicization, and combat the Woke agenda. If implemented, this plan would profoundly impact how the U.S. government operates, promoting a more efficient, limited government aligned with conservative principles. Threat to the Democratic Deep State: A potential new administration under Donald Trump represents an existential threat to the Democratic Deep State entrenched in American institutions. The dissolution of the DHS, depoliticization of intelligence agencies, division of the Secret Service, review of Executive Order 12333, privatization of the TSA, and the hiring of employees aligned with conservative values are all measures that would significantly weaken centralized control and the ability to use these institutions for political purposes. By dismantling concentrated power and promoting a more transparent and accountable government, Project 2025 aims to restore public trust and ensure that government agencies serve national interests rather than partisan ones. Of course, not all aspects of the plan may be implemented, but the prospect of several of these measures being enacted should be a cause for concern for the Democratic Deep State.
-
 @ ff1a68c4:ec9831cf
2024-10-24 14:49:33
@ ff1a68c4:ec9831cf
2024-10-24 14:49:33Año 2147. La misión de la nave Odisea VII tenía como objetivo estudiar las lunas de Júpiter. Nadie esperaba que se encontraran con lo que estaba a punto de revelar el gigante gaseoso. A bordo, cinco astronautas, expertos en astrobiología y física cuántica, orbitaban el coloso, maravillados por sus tormentas eternas y sus mares de hidrógeno líquido.
Durante meses, la tripulación había lanzado sondas y drones a través de la atmósfera turbulenta, recogiendo datos imposibles de descifrar. Era como si el planeta se resistiera a la intrusión, ocultando secretos detrás de las franjas de nubes y la Gran Mancha Roja.
El comandante Foster, junto con la doctora Elena Ivankov, detectaron una anomalía: un patrón en las corrientes eléctricas de Júpiter que parecía regular, como un latido. Al principio, lo atribuyeron a fenómenos naturales, pero la regularidad era inquietante. Eran pulsaciones precisas, organizadas, como los de un corazón titánico, aunque tan lentas que requerían equipo especializado para percibirlas.
“Esto no es solo una tormenta más”, murmuró Elena frente a la pantalla holográfica. “Es… es un ciclo controlado.”
El equipo empezó a conectar las piezas. Las corrientes de viento y los campos magnéticos de Júpiter no se movían al azar; parecían responder a la posición de otros planetas en el sistema solar. Cada vez que la gravedad de Saturno o Marte interactuaba con Júpiter, las pulsaciones cambiaban, como si ajustara su frecuencia para estabilizar las órbitas.
Foster frunció el ceño, ajustando sus datos en el simulador gravitacional. “Si estos latidos controlan la dinámica del sistema solar, ¿qué pasaría si se detuvieran?”
“Ningún planeta sobreviviría”, respondió Ivankov, con los ojos fijos en la pantalla.
Fue entonces cuando tomaron la decisión más osada de la misión: enviar una sonda mucho más profunda de lo que cualquier nave había llegado antes, para penetrar en las capas interiores de Júpiter. Las sondas anteriores habían sido destruidas, pero esta nueva, equipada con inteligencia cuántica adaptativa, podía reaccionar a los cambios a una velocidad inimaginable. La llamaron Ecos.
Cuando Ecos descendió, las lecturas empezaron a volverse más extrañas. Júpiter parecía estar "sintiendo" la presencia de la sonda. Las pulsaciones aumentaron, y el campo magnético se distorsionó. Ecos transmitió imágenes de lo que se encontró en el núcleo del planeta: una estructura titánica, más grande que cualquier ciudad humana, compuesta de una sustancia orgánica fusionada con energía pura.
"¿Estás viendo lo mismo que yo?", susurró Foster, incapaz de procesar lo que estaba ante sus ojos.
Ivankov asintió en silencio, sus dedos temblando sobre el teclado. "Júpiter… no es solo un planeta. Es un organismo vivo."
La tripulación permaneció en silencio mientras la sonda transmitía imágenes y datos. Era como si el planeta mismo estuviera compuesto de órganos que regulaban la estabilidad gravitacional del sistema solar. Un ser inconcebible, de una escala tan vasta que su única función era equilibrar fuerzas cósmicas. Cada tormenta, cada rayo, cada pulso magnético, todo formaba parte de su regulación.
"Este 'ser' mantiene el equilibrio", reflexionó el comandante, su voz era apenas un susurro entre el zumbido de los sistemas de la nave. "Si interfiéramos demasiado, podría romper la frágil danza de los planetas."
La doctora Ivankov, profundamente impactada, sugirió la teoría más radical: "Júpiter no solo es consciente… sino que actúa como una especie de guardián del sistema solar. Un ser con un propósito tan simple como vasto: mantener el equilibrio entre los cuerpos celestes. Si alguna anomalía cósmica amenazara el equilibrio, Júpiter respondería, ajustando las órbitas, corrigiendo las trayectorias."
Entonces llegó la transmisión final de Ecos: "Interferencia detectada. Estructura orgánica ha reconocido nuestra presencia. Cambios en los latidos. Aumento de la presión. Reacción… inminente."
El corazón de Júpiter había comenzado a acelerarse.
"No deberíamos haber venido tan lejos", dijo Foster, tomando el mando de la nave. "Es un ser que no entiende nuestras intenciones. Lo único que sabe es que estamos perturbando el equilibrio."
Con los latidos de Júpiter resonando en sus oídos, la tripulación inició una retirada rápida, temiendo que cualquier alteración en ese organismo colosal pudiera desestabilizar el sistema solar entero.
Mientras se alejaban, observaron cómo las tormentas del gigante gaseoso volvieron a la calma, y el pulso volvió a estabilizarse.
"Júpiter sigue latiendo", susurró Ivankov, mirando la vasta esfera a lo lejos.
Quizás, pensó la tripulación, no era el momento para que la humanidad supiera demasiado sobre su lugar en la delicada danza del cosmos.
-
 @ 129f5189:3a441803
2024-09-09 23:11:19
@ 129f5189:3a441803
2024-09-09 23:11:19Precious metals have served as monetary backing for millennia, but this does not guarantee that gold is a safe investment or a good hedge against economic crises and monetary collapses. Since its last major rally in the 1980s, gold has been progressively demonetized. Those who acquired gold in the late 1980s will need to rely on a significant increase in demand or a supply shock for its price to rise by 561% and regain the purchasing power it had 40 years ago. https://image.nostr.build/dd5fec2b474ea34cd72ddf5781393b528e63a358d523c9428f3ba4649f4f42aa.jpg If you look at the purchasing power of $1 (green line), you'll see that the depreciation is even faster. This might create the impression that gold is a good store of value. But does the fact that something loses value more slowly amidst a general decline really make it a store of value? Unless the total demand for gold increases at the same rate as its supply has grown in recent years, the purchasing power of the metal is likely to decline. https://image.nostr.build/9f24f6cf37780fe851746057520064ed94acd96547be53bd341c9e15b8762773.jpg In other words, if you own an ounce of gold, that ounce will represent an increasingly smaller fraction of the total gold reserves, meaning you are being diluted. Additionally, one should also consider the cost and risk of storage, but that's another issue. If you don't want to compare the purchasing power of gold today with the 1980s, you can consider its value from 9 years ago. Between September 2011 and November 2015, the Fed printed approximately $2.8 trillion. This also provides a perspective on gold's depreciation relative to the significant monetary expansion during that period. https://image.nostr.build/822e0a861e16ca258e0427875a84b5c8e5420e51bcf65674b453b55ed78edefd.jpg In other words, the Fed expanded its monetary base by about 30% during that 4-year period. However, the price of an ounce of gold fell by 45% (from $1,900 to $1,057) over the same interval. A true store of value should protect against excessive money printing. In contrast, during that same period, Bitcoin appreciated by 8,500% (from $5 to $419). https://image.nostr.build/32a7ca39a6e69e2780f9ab49390c7b7380499fcfe54ae4ef693e6fc91686a41e.jpg Indeed, while it is interesting to note that this was the exact period when gold derivatives were launched on CME Group, it's important to remember that correlation does not imply causation. Many factors can influence the price of gold and Bitcoin, and establishing a direct causal relationship requires more detailed analysis. https://derivsource.com/2011/06/21/cme-group-announces-the-launch-of-three-new-short-term-gold-crude-oil-and-natural-gas-options-contracts/ In an asset where supply can only be physically verified, flooding the market with gold contracts could lead to significant issues. This might result in market manipulation, legal liabilities, fines, and potentially even imprisonment for those involved. Such actions can undermine the integrity of the market and lead to regulatory and legal consequences. https://www.cnbc.com/2018/11/06/ex-jp-morgan-trader-pleads-guilty-to-manipulating-metals-markets.html Over longer periods, gold has not functioned as a true "store of value" relative to the dollar for quite some time, despite recently returning to its price from 9 years ago. This suggests that, while gold may have periods of price recovery, it has struggled to maintain its value over extended horizons compared to fiat currencies. It's worth noting that before 1980, aluminum was valued higher than gold. This reflects how market dynamics and technological advancements can significantly impact the value of commodities over time. https://www.mgsrefining.com/blog/why-aluminum-is-no-longer-a-precious-metal/ While gold has been undergoing a gradual demonetization process since 1980, another asset appears to be experiencing the opposite—hyper-monetization. (See in red; don't be alarmed.) https://image.nostr.build/435a5369f778a7be727b50e4c6328cfc353240bf804e1ed69313b9a8e1233f7e.jpg With the advent of Bitcoin, you believe that gold will continue on the same path as silver since the end of the bimetallic standard in 1853: a prolonged process of demonetization, with increasing volatility and reduced liquidity. https://image.nostr.build/5b9c8bfdb09e51d639e380df160c98beb9ee1d917ea13d28ef67711cfa5f8086.jpg Since 1913, the dollar has lost 97% of its purchasing power. Over the same period, the gold supply has increased significantly. Since 1980, gold has lost about 82% of its purchasing power. Given that the dollar is used as the unit of account and gold's liquidity is measured in dollars, these changes reflect the complex interaction between the currency and the precious metal. The U.S. is by far the country with the largest gold reserves in the world and is also the fourth-largest miner of the metal. Additionally, the country controls and issues the currency that serves as the unit of account for gold and has the highest liquidity in global trade. Is gold easy to transport? Is it simple to verify its supply and authenticity? Is it practical to store? Is its industrial utility significant? Can it be disrupted? And what about the continuous increase in its supply? These are important questions to consider. In my humble opinion, it will not be the dollar or fiat currencies that will suffer the most from the existence of Bitcoin, but rather the market cap of gold. https://image.nostr.build/61dddefabc4b69f784631a3294bdd978e3411bba40fb52d585e13b48002389fe.jpg
-
 @ e83b66a8:b0526c2b
2024-09-09 20:30:30
@ e83b66a8:b0526c2b
2024-09-09 20:30:30We have a confession to make. NOSTR is not perfect, we are still building. No client you use does everything you want it to, and everything it does is imperfect.
Therefore, I strongly advise you to run multiple clients.
On iPhone, I run: Damus: https://nostrapps.com/damus Primal: https://primal.net/downloads Nostur: https://nostrapps.com/nostur
On Android I run: Primal: https://primal.net/downloads Amethyst: https://nostrapps.com/amethyst
On desktop I run: Primal: https://primal.net/downloads noStrudel: https://nostrapps.com/nostrudel
Also, because I run a node (Umbrel & Start9), I self host noStrudel on my own relay.
If you haven’t taken the plunge to run a node, now might be a good time to think about it.
There are many, many options for clients, the “Social” section of https://nostrapps.com/
lists 23 currently.
Play with them, see what they do, if you’re a developer, you could even consider building or forking your own.
Have fun and realise we are building freedom tech, not just running it.
-
 @ 06639a38:655f8f71
2024-10-24 14:49:08
@ 06639a38:655f8f71
2024-10-24 14:49:08Project Name
Nostr
Project Description
Nostr (Notes and Other Stuff Transmitted by Relays) is an open, censorship-resistant, and decentralized communication protocol designed for simplicity and resilience. Unlike traditional platforms, Nostr doesn’t rely on centralized servers. It already supports various use cases with free, open-source clients—offering alternatives to platforms like Twitter/X, Meetup.com, Excel 365, healthcare system and more. We will help you get started with Nostr.
Nostr has seen remarkable adoption and growth within the open-source community, evidenced by over 12,500 GitHub stars, 500+ forks, and contributions from more than 350 developers. The protocol has catalyzed the creation of an impressive ecosystem of over 390 projects, including mobile and web clients, relays, tools, and services that further enhance Nostr’s functionality. With over 70 tools and 48 libraries, developers can integrate Nostr into a wide array of applications—ranging from chat platforms to file storage and even decentralized marketplaces. These resources help to build decentralized, censorship-resistant systems without the need for centralized servers. Whether you’re working on peer-to-peer markets, privacy-focused messaging apps, or decentralized social media, Nostr’s ecosystem offers the tools.
Project website
https://github.com/nostr-protocol
Source code
https://github.com/nostr-protocol/nips
Project Theme
World Wide Web
Do you want a stand for the entire event or just for one day?
Entire event
Why do you want to be at FOSDEM?
We want to be at FOSDEM because it’s the perfect place to connect with like-minded developers and open-source enthusiasts who share our passion for decentralization, innovation, and building open permissionless technologies. FOSDEM fosters collaboration and the growth of community-driven projects and Nostr is a natural fit as a real grassroots project with its open protocol and commitment to build communication technology with resilience and simplicity in mind.
By being at FOSDEM, we aim to raise awareness, share knowledge and inspire others to explore the potential of decentralized communication systems. We also want to engage with the FOSS community and gain feedback to help Nostr grow. If people are really interested in how they can use Nostr we will show the possibilities, demo existing clients and provide in-depth explanations of how the protocol can replace the social layer (with user accounts in living a database) in existing software.What is the relation between the project and the primary contact?
Jurjen works with the community to promote its development, onboard new developers, and contribute to its open-source ecosystem. My role includes helping to raise awareness of Nostr's potential, organizing events, and supporting adoption by providing educational resources and technical guidance.
What is the relation between the project and the secondary contact?
Sebastian (37) is an independent creative / fullstack web developer who is the maintainer of a PHP helper library supported by OpenSats. Besides this project he is also making contributions with developing Nostr modules for Drupal.
“Since I've been online on the internet (1998), I'm highly interested in online communities, social networking and new ways of digital interactions. The internet has changed radically in the last decade and that change is not serving our interests. It's fair to say the web is broken in many ways. With Nostr we can fix this.”Social media links
npub1l77twp5l02jadkcjn6eeulv2j7y5vmf9tf3hhtq7h7rp0vzhgpzqz0swft(Jurjen)
npub1qe3e5wrvnsgpggtkytxteaqfprz0rgxr8c3l34kk3a9t7e2l3acslezefe(Sebastian)
npub1hz5alqscpp8yjrvgsdp2n4ygkl8slvstrgvmjca7e45w6644ew7sewtysa(Tanja)
npub1nkmta4dmsa7pj25762qxa6yqxvrhzn7ug0gz5frp9g7p3jdscnhsu049fn(Kevin)Anything else you like to add?
We’d also like to highlight that Nostr was created by Fiatjaf, an anonymous founder, which aligns with its principles of openness and decentralization. As an open protocol, Nostr is designed to evolve and find its own way, just like the foundational protocols of the internet. Importantly, Nostr is not a blockchain project—there are no tokens, no costs, and no barriers. It’s also not a platform nor a NFT. It’s purely decentralized, built for resilience and simplicity. While payment solutions like Bitcoin can be integrated, they are optional, not intrinsic to the protocol. This makes Nostr accessible and flexible, truly embodying the spirit of the open internet.
Nostr is more than just a technological protocol; it’s about the energy, problem-solving, and sense of hope that draws people in. Even newcomers can play a significant role in the ecosystem, gaining insight from the outside while discovering the protocol’s potential. Tanja, for example, isn’t from a tech background, yet after just three months, she’s taken on a major organizational role. She’s been spreading the message of freedom of speech and is leading the Nostr Booth LATAM tour, where volunteers, entrepreneurs, and Nostr-based businesses come together, supported by the entire community, to raise awareness about Nostr. Her passion for decentralization and open collaboration also drives her efforts to bring Nostr to FOSDEM, where she will help connect the project with like-minded developers and open-source advocates.
Please reach out to us if there are any questions. We’re really looking forward to presenting Nostr as a protocol at one of the best places where free and open-source software is flourishing.
This content will be used for a FOSDEM stand submission via https://pretalx.fosdem.org/fosdem-2025-call-for-stands/
-
 @ e83b66a8:b0526c2b
2024-09-09 20:27:41
@ e83b66a8:b0526c2b
2024-09-09 20:27:41First,
Key management.
When you “created” your NOSTR account, what you actually created was a cryptographic key pair. This consists of a private key, which starts “nsec” and a public key which starts with “npub”.
As the names suggest, your “nsec” key is private and you should never reveal it to anyone. Your “npub” key is your public key, feel free to share that everywhere.
Your “npub” key is used by others to verify your identity, through the signature added to your messages. It is also used by others to encrypt private messages to you.
We don’t have perfect key management yet and because of the limitation of smart phones and various eco systems, it often becomes necessary for you to copy and paste your private key into apps in order to use them. This is less than ideal, but until we have ubiquitous cross platform key management devices, this situation will remain necessary.
For the moment, consider using software key management options, some of which are listed under “signers” here: https://nostrapps.com/
N.B. We do have projects like Seedsigner that provide more secure hardware key management, but this isn’t for the faint hearted:
Secondly,
Lightning wallets.
It is common for most people to link a Bitcoin Lightning wallet to their NOSTR profile
N.B. Your profile is stored on relays and signed by your private key, which is verified by others through your public key.
You are not tied to any specific wallet for sending payments (called zaps), but you do provide a specific incoming LN address for receiving payments. This could be something like a wallet of Satoshi Address i.e. “randomname@walletofsatoshi.com” or could you be your own node with a connection to it via “Nostr Wallet Connect” a free plugin that connects a lightning wallet.
Enabling this allows people to “zap” any posts or content or even send you payments directly at any time or for any reason. N.B. It is called freedom money for a reason….
It also allows you to send small micropayments to posts or people you like.
Thirdly,
Paid Services
As you go deeper into the NOSTR ecosystem, you’ll notice there is no advertising being pushed at you and there are no algorithms manipulating the content you receive. This is because there is no company behind NOSTR, it is a protocol. Because of this, while all the ecosystem is free to use and will remain so for the foreseeable future, most of it is run by enthusiastic volunteers or developers and incurs a cost to them. For that reason many of us choose to support these #devs by paying for services. This can also enhance our experience, giving our “npub” greater reach and discoverability.
I, for example choose to pay for the following services:
https://nostr.wine/ - 120,000 Sats for 2 years relay https://relay.tools/ - My own relay - https://nortis.nostr1.com/ 12,000 Sats a month https://nostr.build/ - Media storage - 69,000 Sats for 1 year
Total: 22,750 Sats per month Approx $15 per month
This is not strictly necessary, but I decided to support the various developers behind these projects.
Do not feel any pressure at this early stage to pay for any service, but if you enjoy the freedom NOSTR brings, you may want to consider supporting the projects that become important to you going forward.
-
 @ ff1a68c4:ec9831cf
2024-10-24 14:47:03
@ ff1a68c4:ec9831cf
2024-10-24 14:47:03En un mundo en constante evolución, la ciencia nos ofrece valiosas herramientas para mejorar nuestra calidad de vida y prevenir enfermedades neurodegenerativas como la demencia. A partir de los consejos de especialistas y datos de estudios recientes, he reunido una síntesis de enfoques clave que coinciden en varios puntos esenciales. Aquí te presento un resumen práctico:
El modelo MEDALS: Los pilares del bienestar
El acrónimo MEDALS nos recuerda los aspectos fundamentales que pueden ayudar a mantener una buena calidad de vida:
- Meditación: La práctica regular de la meditación reduce el estrés, mejora la concentración y contribuye a un mayor bienestar emocional.
- Ejercicio: El movimiento es vital para la salud física y mental. Mantener una rutina de ejercicio regular no solo fortalece el cuerpo, sino también el cerebro.
- Dieta: Una alimentación equilibrada es clave. Optar por una dieta rica en nutrientes, como la mediterránea, promueve un cerebro saludable.
- Apreciación: Practicar la gratitud y el aprecio por las pequeñas cosas de la vida puede elevar nuestro bienestar emocional y mental.
- Love (amor) y Learning (aprendizaje): Mantener vínculos afectivos y relaciones cercanas fortalece la mente. El aprendizaje continuo mantiene el cerebro activo y en constante crecimiento.
- Sueño: Dormir lo suficiente y de forma reparadora es crucial para la regeneración cerebral y la memoria.
Manantiales de la fuerza interior: Una guía integral para el bienestar
Otra perspectiva ofrece una visión holística de cómo cuidar cuerpo y mente. Estos son los cinco manantiales de energía interior que contribuyen a un estado óptimo de bienestar:
- Sueño profundo y reparador: Un buen descanso nocturno es el pilar del equilibrio físico y mental.
- Alimentación sana e hidratación: Mantener una dieta nutritiva y una adecuada hidratación es esencial para el buen funcionamiento del cerebro y del cuerpo.
- Respiración consciente: Practicar ejercicios de respiración ayuda a reducir el estrés y aumenta la claridad mental.
- Ejercicio y relajación: Alternar entre actividad física y momentos de descanso es fundamental para evitar el agotamiento.
- Actitud mental positiva: Mantener una mentalidad optimista y enfocada en el crecimiento nos ayuda a enfrentar mejor los retos de la vida.
6 Reglas anti-demencia: Proteger el cerebro a largo plazo
Algunos expertos proponen un enfoque más específico para la prevención de la demencia:
- Vínculos sociales: El cerebro es un órgano social. Mantener relaciones cercanas y participar en actividades grupales es clave para su salud.
- Ejercicio físico: El cuerpo y la mente están conectados. La actividad física regular mejora el rendimiento cerebral.
- Curiosidad y aprendizaje continuo: Mantener el cerebro activo con nuevos intereses y aprendizajes es crucial para prevenir su deterioro.
- Buena alimentación: Optar por alimentos ricos en Omega-3 y seguir una dieta mediterránea favorece la salud cerebral.
- Manejo del estrés: El estrés crónico es un enemigo del cerebro. Aprender a relativizar las situaciones y ver los desafíos como oportunidades puede reducir su impacto.
- Dormir bien: Un sueño adecuado es esencial para la reparación y el funcionamiento óptimo del cerebro.
Hallazgos de The Lancet: Factores modificables y no modificables en la prevención de la demencia
Uno de los estudios más importantes sobre la prevención de la demencia, publicado en The Lancet, destaca los factores modificables que pueden influir en nuestro futuro cognitivo:
- Formación continua: Aprender y mantenerse intelectualmente activo durante toda la vida puede retrasar el deterioro cognitivo.
- Cuidado de la audición: Proteger la audición desde la juventud es crucial. En la vejez, el uso de audífonos puede ayudar a mantener el estímulo auditivo.
- Salud emocional: El estrés crónico, la ansiedad y la depresión son factores de riesgo importantes para el desarrollo de la demencia.
- Ejercicio físico y salud metabólica: Evitar el sedentarismo, el sobrepeso, la diabetes y los niveles elevados de colesterol LDL reduce el riesgo de enfermedades neurodegenerativas.
- Protección contra golpes en la cabeza: Los traumatismos craneales aumentan el riesgo de demencia. Protegerse es fundamental.
- Reducción de tóxicos: Evitar el tabaco, el consumo excesivo de alcohol y la exposición a contaminantes ayuda a preservar la salud cerebral (ej. filtros para el aire o en la llave del agua)
- Vida social activa: El aislamiento social es un factor de riesgo para la demencia. Mantenerse involucrado en grupos y actividades sociales es clave.
- Suplementos: Aunque no son esenciales, algunos suplementos como arándanos, vitamina D, Omega-3, y magnesio pueden ser beneficiosos en casos de deficiencia.
Implementar estos principios no solo mejorará la calidad de vida en el presente, sino que también reducirá significativamente el riesgo de desarrollar demencia en el futuro. Vivir de manera consciente, cuidar el cuerpo y nutrir la mente son las claves para una vida larga y saludable.
-
 @ d5c3d063:4d1159b3
2024-10-24 14:37:08
@ d5c3d063:4d1159b3
2024-10-24 14:37:08ปรัชญา อาวุธแห่งเหตุผลและเสรีภาพในโลกแห่งความขัดแย้ง
https://image.nostr.build/b3e2278447703b23c18d6b8dd98986b700958acbbe06b3cca6ce7efa55b6c1ad.jpg
โลกที่เราอาศัยอยู่เปรียบเสมือนสมรภูมิแห่งความคิด แนวคิดต่างๆ ถูกนำมาถกเถียงและท้าทายอยู่เสมอเพื่อค้นหาและพิสูจน์ความจริง ความขัดแย้งนี้ปรากฏชัดในหลายมิติ เช่น การปะทะกันระหว่างเหตุผลกับความงมงาย เสรีภาพกับการถูกบังคับ ปัจเจกนิยม (Individualism) กับลัทธิรวมหมู่ (Collectivism) และทุนนิยมกับสังคมนิยม ท่ามกลางความสับสนวุ่นวายนี้ ปรัชญาทำหน้าที่เสมือนป้อมปราการแห่งเหตุผลและเสรีภาพ เป็นเครื่องมือสำคัญที่ช่วยให้เราเข้าใจและวิเคราะห์โลกที่เต็มไปด้วยความขัดแย้ง พร้อมกับนำทางชีวิตของเราอีกด้วย .
ปรัชญาในบริบทนี้ มิใช่เพียงแสงเทียนริบหรี่ในห้องสมุด หากแต่เป็นอาวุธแห่งเหตุผล ที่ใช้ในการต่อสู้กับความคิดที่บิดเบือนและการใช้อำนาจในทางที่ผิด เพื่อปกป้องและส่งเสริมเสรีภาพของมนุษย์ มันคือดาบเพลิงที่ลุกโชนในสนามรบแห่งความคิดที่ช่วยให้เรามองทะลุผ่านมายาคติ ความเชื่อที่ไร้เหตุผล และการโฆษณาชวนเชื่อ ทั้งยังช่วยให้วิเคราะห์ข้อมูลอย่างมีวิจารณญาณและตัดสินใจบนพื้นฐานของหลักฐานและตรรกะ นำไปสู่การเข้าถึงความจริง ตัวอย่างที่เห็นได้ชัดคือการเซ็นเซอร์ข้อมูลข่าวสาร ซึ่งถูกใช้เป็นเครื่องมือในการบิดเบือนข้อมูล ปลุกปั่นอารมณ์ เป็นการใช้อำนาจในทางที่ผิด ปิดกั้นการเข้าถึงความจริง เพื่อควบคุมความคิดของประชาชน .
หัวใจสำคัญของปรัชญาคือ การใช้เหตุผล หลักฐาน และตรรกะ ในการแสวงหาความจริง เพื่อนำไปสู่ การตัดสินใจที่ถูกต้อง ปรัชญาฝึกฝนให้เรามีวิจารณญาณ ไม่หลงเชื่ออะไรง่ายๆ และไม่ยอมรับความคิดเห็นใดๆ โดยปราศจากการตรวจสอบอย่างถี่ถ้วน ปรัชญาสอนให้เราตั้งคำถาม เช่น ใครเป็นคนพูด ? มีหลักฐานอะไรสนับสนุน ? มีมุมมองอื่น ๆ อีกหรือไม่ ? ข้อสรุปนี้ขัดแย้งกับข้อเท็จจริงหรือหลักการพื้นฐานใด ๆ หรือไม่ ? ก่อนที่จะตัดสินใจเชื่อหรือยอมรับความคิดเห็นใด ๆ เพราะการยอมรับความคิดเห็นโดยไม่ผ่านการไตร่ตรอง อาจนำเราไปสู่การตัดสินใจที่ผิดพลาดและตกเป็นเหยื่อของการบิดเบือน .
ปรัชญายังส่งเสริมความเข้าใจในคุณค่าของเสรีภาพและความสำคัญของปัจเจกบุคคล เสรีภาพในการคิดการแสดงออกและการใช้ชีวิต เป็นสิ่งจำเป็นสำหรับการพัฒนาศักยภาพของมนุษย์ เพื่อการสร้างสรรค์สังคมที่เจริญรุ่งเรือง ปรัชญาช่วยให้เราตระหนักถึงสิทธิและหน้าที่ของตนเองในฐานะปัจเจกบุคคลและเพื่อปกป้องเสรีภาพเหล่านี้จากการถูกคุกคามจากอำนาจรัฐหรือแนวคิดแบบคติรวมหมู่ สังคมที่มีความยุติธรรมมีเสรีภาพและมีความเจริญรุ่งเรือง คือสังคมที่เคารพในสิทธิและเสรีภาพของปัจเจกบุคคลที่ส่งเสริมการใช้เหตุผลนั้น ล้วนมีรากฐานอยู่บนระบบเศรษฐกิจแบบทุนนิยม เพราะทุนนิยมเป็นระบบที่สอดคล้องกับหลักการเหล่านี้ โดยเปิดโอกาสให้ทุกคนมีส่วนร่วมในการสร้างความมั่งคั่งและเติบโตอย่างอิสระ .
ในโลกที่ความขัดแย้งทางความคิดทวีความรุนแรงและข้อมูลข่าวสารแพร่กระจายอย่างรวดเร็ว ปรัชญามิใช่เพียงทางเลือก แต่เป็นเกราะป้องกันที่ขาดไม่ได้ การศึกษาปรัชญา การฝึกฝนการใช้เหตุผลและการตั้งคำถาม คือการลงทุนที่คุ้มค่าที่สุดสำหรับอนาคต เพราะมันจะช่วยให้เรามีภูมิคุ้มกันต่อการถูกชักจูง การหลอกลวงและการใช้อำนาจในทางมิชอบ เป็นก้าวสำคัญในการสร้างสังคมที่เสรี มีความยุติธรรมและการเจริญรุ่งเรืองอย่างแท้จริง ดังนั้น เวลามีค่า…ศึกษาปรัชญา ฝึกฝนการใช้เหตุผล และอย่าปล่อยให้ความงมงายและอคติครอบงำจิตใจ เพื่อที่เราจะสามารถเป็นผู้กำหนดชีวิตของตนเองได้และใช้ชีวิตอย่างมีอิสระ มีเหตุผล และสร้างสรรค์คุณค่าตามที่เราเลือก เพื่อบรรลุศักยภาพสูงสุดของเราในฐานะปัจเจกบุคคล
Siamstr #Philosophy #ปรัชญา
-
 @ 4ba8e86d:89d32de4
2024-10-24 14:03:14
@ 4ba8e86d:89d32de4
2024-10-24 14:03:14O Collabora Office é uma suíte de escritório baseada em código aberto que oferece uma alternativa viável e de qualidade ao popular pacote Office da Microsoft. Desenvolvido pela Collabora, uma empresa líder em serviços de consultoria e desenvolvimento de software de código aberto, o Collabora Office oferece uma gama completa de aplicativos de produtividade para a plataforma Android, incluindo processador de texto, planilha, apresentação e muito mais.
Recursos e Funcionalidades.
O Collabora Office oferece uma ampla gama de recursos e funcionalidades para dispositivos Android, comparáveis aos encontrados em outras suítes de escritório populares. Além das funcionalidades básicas, como criação e edição de documentos de texto, planilhas e apresentações, o Collabora Office suporta formatos de arquivo comuns, como o formato OpenDocument (ODF) e o formato do Microsoft Office (OOXML). Isso significa que você pode facilmente compartilhar e colaborar em documentos com usuários de outras suítes de escritório.
Uma característica notável do Collabora Office para Android é a capacidade de edição colaborativa em tempo real. Vários usuários podem trabalhar simultaneamente em um documento, visualizando as alterações em tempo real. Isso torna a colaboração em equipe mais eficiente, permitindo que os membros trabalhem juntos em projetos sem a necessidade de trocar arquivos várias vezes.
O Collabora Office para Android possui uma interface intuitiva e fácil de usar, projetada especificamente para dispositivos móveis. Isso garante uma experiência de usuário fluida e permite que os usuários aproveitem ao máximo os recursos e funcionalidades do aplicativo em seus smartphones ou tablets.
Uma das principais vantagens do Collabora Office para Android é o fato de ser baseado em código aberto. Isso significa que o software é desenvolvido de forma transparente e está disponível para qualquer pessoa utilizar, estudar, modificar e distribuir. A natureza de código aberto do Collabora Office traz vários benefícios, incluindo:
-
Custos reduzidos: O Collabora Office para Android é gratuito para download e uso, eliminando a necessidade de licenças caras. Isso é particularmente atraente para pequenas empresas e usuários domésticos que buscam uma alternativa acessível ao pacote Office tradicional.
-
Personalização e flexibilidade: Como o código-fonte está disponível, desenvolvedores e usuários avançados podem personalizar e adaptar o Collabora Office para Android às suas necessidades específicas. Isso permite criar soluções personalizadas e integrar o software a outros sistemas e fluxos de trabalho existentes.
-
Segurança: Com a comunidade de código aberto constantemente analisando e auditando o software, eventuais vulnerabilidades de segurança são identificadas e corrigidas rapidamente. Além disso, os usuários podem ter maior confiança na privacidade de seus dados, uma vez que podem verificar como o software lida com as informações.
O Collabora Office para Android é uma alternativa sólida e de código aberto ao pacote Office da Microsoft. Com recursos abrangentes, capacidade de edição colaborativa em tempo real e uma interface otimizada para dispositivos móveis, ele se tornou uma escolha popular entre empresas e usuários individuais que desejam uma solução de produtividade acessível e personalizável para seus dispositivos Android. Além disso, a natureza de código aberto do Collabora Office traz vantagens significativas, como custos reduzidos, flexibilidade e segurança aprimorada. Se você está em busca de uma alternativa confiável e gratuita ao pacote Office tradicional para Android, vale a pena considerar o Collabora Office como uma opção viável.
https://www.collaboraoffice.com/
https://github.com/CollaboraOnline/online
-
-
 @ c11cf5f8:4928464d
2024-09-09 18:45:16
@ c11cf5f8:4928464d
2024-09-09 18:45:16originally posted at https://stacker.news/items/678432
-
 @ e968e50b:db2a803a
2024-09-09 18:21:54
@ e968e50b:db2a803a
2024-09-09 18:21:54Open the frozen pizza bay doors, Hal.
originally posted at https://stacker.news/items/678403
-
 @ 4ba8e86d:89d32de4
2024-10-24 13:52:57
@ 4ba8e86d:89d32de4
2024-10-24 13:52:57Tecnologia de escalonamento #Bitcoin Layer-2 baseada no conceito de statechains, que permite que chaves privadas para depósitos BTC (UTXOs) sejam transferidas com segurança entre proprietários fora da cadeia.
Mercury Layer é uma implementação de um protocolo statechain de camada 2 que permite a transferência e liquidação fora da cadeia de saídas de Bitcoin que permanecem sob a custódia total do proprietário o tempo todo, enquanto se beneficia de transações instantâneas e de custo zero. A capacidade de realizar esta transferência sem exigir a confirmação (mineração) de transações em cadeia tem vantagens em uma variedade de aplicações diferentes.
um sistema de transferência e controle de propriedade do Bitcoin, especificamente focado em saídas de transações não gastas (UTXOs),
um resumo detalhado dos principais elementos e procedimentos do sistema:
-
Saída de Transação Não Gasta (UTXO): UTXO é a unidade fundamental que representa valor e propriedade no Bitcoin. Cada UTXO é identificado por um ID de transação (TxID) e um número de índice de saída (n) e possui duas propriedades essenciais: valor em BTC e condições de gasto, definidas em um Script. As condições de gasto geralmente envolvem uma chave pública que requer uma transação assinada com a chave correspondente.
-
Transferência de Propriedade sem Transação On-Chain: O sistema permite a transferência de propriedade de UTXOs controlados por uma única chave pública (P) de uma parte para outra sem a necessidade de executar transações na cadeia (on-chain) do Bitcoin ou alterar as condições de gasto. Isso é facilitado por um mecanismo chamado "Statechain Entity" (SE).
-
Compartilhamento de Chave Privada: A chave privada (s) para a chave pública P é compartilhada entre o SE e o proprietário. No entanto, nenhuma das partes conhece a chave privada completa. Isso requer cooperação entre o proprietário e o SE para gastar o UTXO.
-
Atualização/Transferência de Chave: A propriedade do UTXO pode ser transferida para um novo proprietário através de um processo de atualização de chave. Isso envolve a substituição do compartilhamento de chave privada do SE para que corresponda ao compartilhamento de chave do novo proprietário, tudo sem revelar compartilhamentos de chave ou a chave privada completa.
-
Transações de Backup: Além da transferência de propriedade, o sistema inclui transações de backup que podem ser usadas para reivindicar o valor do UTXO pelo atual proprietário, caso o SE não coopere ou desapareça. Essas transações são assinadas cooperativamente pelo proprietário atual e pelo SE e possuem um bloqueio de tempo (nLocktime) que permite a recuperação dos fundos em uma altura de bloco futura especificada.
-
Mecanismo de Redução do Backup de Timelock: Para limitar o número de transferências possíveis durante um período de tempo, o sistema utiliza um mecanismo de decremento do nLocktime. O usuário é responsável por enviar as transações de backup no momento adequado.
-
Cadeias Estaduais (Statechains): O sistema opera usando cadeias estaduais, que são uma camada adicional que permite a transferência de propriedade de UTXOs. O SE precisa seguir o protocolo, mas não armazena informações sobre compartilhamentos de chave anteriores.
-
Cegagem (Blinding): O servidor da camada Mercury (SE) é cego, o que significa que não tem conhecimento das moedas que está assinando. Isso é alcançado através do uso de criptografia de chave pública para ocultar informações de chave privada compartilhada entre as partes.
-
Protocolo de Camada Mercury: O protocolo detalha os procedimentos desde o depósito inicial até a transferência de propriedade, atualizações de chave, retiradas ordenadas e recuperação de backup.
-
Recuperação de Backup: Caso o SE não coopere ou desapareça, o proprietário atual pode recuperar os fundos, enviando a transação de backup quando o nLocktime for atingido.
-
Publicação de Compartilhamento de Chaves: O SE não tem acesso aos IDs de transação individuais das moedas, mas publica compartilhamentos de chaves públicas para cada moeda na lista de ativos. Essa lista é comprometida com a blockchain para provar a exclusividade da propriedade.
Este sistema é projetado para fornecer uma maneira segura e eficiente de transferir e controlar a propriedade do Bitcoin, permitindo a recuperação de fundos em caso de problemas com o servidor.
No sistema de controle de propriedade de saídas de transações não gastas (UTXOs), cada UTXO é uma chave compartilhada composta por duas partes: o proprietário e o servidor de compartilhamento. Juntos, eles colaboram para criar transações de backup com bloqueio de tempo, que transferem a propriedade da UTXO para o novo proprietário. Durante essa transferência, a chave pública compartilhada permanece inalterada, mas o compartilhamento da chave do servidor é atualizado por meio de um Protocolo de Computação Multifuncional (MPC) para se alinhar apenas com o novo proprietário. Essa atualização resulta na criação de uma nova transação de backup, direcionada à chave pública do novo proprietário, com um tempo de bloqueio mais curto.
A confiabilidade do servidor é essencial, pois ele é responsável por excluir o compartilhamento de chave anterior. Isso garante que não seja possível conspirar com os proprietários anteriores. O proprietário atual pode gastar a UTXO a qualquer momento, desde que o faça em cooperação com o servidor. No entanto, se o servidor for desligado ou desaparecer, o proprietário atual deve aguardar até que o tempo de bloqueio expire antes de enviar sua transação de backup.
É importante ressaltar que o remetente nunca possui a chave privada completa; ele possui apenas uma parte do compartilhamento. Assim, todas as transações requerem a assinatura conjunta do servidor. Quando a UTXO é transferida para um novo proprietário, o compartilhamento do servidor é atualizado para que ele não possa mais assinar em nome do proprietário anterior, apenas em nome do novo proprietário. Esse sistema de transações de backup com bloqueio de tempo é projetado para proteger contra cenários de não cooperação ou apreensão do servidor, garantindo a segurança das UTXOs e a integridade da rede.
https://github.com/layer2tech/mercury-wallet
https://mercurylayer.com/
https://twitter.com/TTrevethan/status/1689929527420387328?t=0f5oF6w_ZRjWRYGah3HX8Q&s=19
-
-
 @ 9e69e420:d12360c2
2024-10-24 13:10:08
@ 9e69e420:d12360c2
2024-10-24 13:10:08Kamala Harris delivered a sharp critique of Donald Trump, comparing him to Adolf Hitler during a recent speech. She referenced comments made by former Chief of Staff John Kelly, who disclosed that Trump expressed admiration for Hitler while in office.
![Kamala Harris] (https://i.nostr.build/iyRm5cJo9YuRgh3M.png)
Harris stated, "It is deeply troubling and incredibly dangerous that Donald Trump would invoke Adolf Hitler."
She warned that if re-elected, Trump could seek unchecked power and compare him to a dictator. Harris emphasized the importance of understanding Trump's intentions and the implications for America’s future. Her remarks coincided with the fast-approaching election, intensifying her campaign's rhetoric against Trump.
-
 @ 6bae33c8:607272e8
2024-09-09 16:07:43
@ 6bae33c8:607272e8
2024-09-09 16:07:43I’ll write a separate Week 1 Observations later, but I wanted to dedicate this space solely to mourning my Circa Survivor entry.
Circa Survivor costs $1000 to enter and has a $10M prize for the winner, usually split by several as things get down to the wire. Three years ago, when the prize was $6M Dalton Del Don and I — the first time we ever entered — made it to the final 23 in Week 12. The value of our share was something like $260K at that point, but we got bounced by the Lions who beat the 12-point favored Cardinals and took home nothing.
When you enter a large survivor pool, the overwhelming likelihood is you’ll meet this fate at some point, whether in Week 1 or 12. So it’s not really the loss that’s painful, so much as not getting to live and die each week with a chosen team. You lose your status as “the man in the arena whose face is marred by dust and sweat and blood” and become just an observer watching and commentating on the games without the overarching purpose of surviving each week.
This year was also different due to the lengths to which I went to sign up. It’s not just the $1000 fee, it’s getting to Vegas in person, the $400 in proxy fees (you need locals to input your picks for you if you don’t live there), the $60 credit card fee, the $200 crappy hotel I booked at the last minute, the flights (one of which was cancelled due to heat), the rental car that necessitated, the gas, getting lost in the desert, the entire odyssey while sick and still jet-lagged in 122-degree heat.
But it’s not about the money, and it’s not even about the herculean effort per se, but the feeling and narrative I crafted around it. I was the guy who got this done. I flew from Portugal to San Francisco for 12 hours, two days later from SF to Palm Springs to help my 87-YO uncle with his affairs, improvised to get from Palm Springs to Vegas, which took six hours due to road closures, signed up for the contests, made the flight back to San Francisco, flew to Denver at 7 am the next day, took my daughter the Rockies game in the afternoon and then on to Boulder the following day. Maybe that’s not so impressive to some of you, but for me, an idle ideas person, a thinker, observer, someone who likes to express himself via a keyboard, it was like Alexander the Great conquering Persia.
And it’s not only about that smaller mission, or the narrative I crafted around it, but a larger one which was to bring sports content to nostr which I vowed to do before the summer which is why I felt I had to make the effort to get to Vegas to sign up for the contests, to have sufficient skin in the game, to have something real about which to write.
And I got the idea to do this seriously because Heather wrote a guide to Lisbon which I posted on nostr, and a few prominent developers there were surprisingly excited about getting that kind of quality content on the protocol. And I thought — if they’re this excited about a (very in-depth) guide to one particular city in Europe, how much more value could I create posting about a hobby shared by 50-odd million Americans? And that thought (and the fact I had to go to Palm Springs anyway) is what set me off on the mission in the first place and got me thinking this would be Team of Destiny, Part 2, only to discover, disappointingly, it’s real destiny was not to make it out of the first week.
. . .
While my overwhelming emotion is one of disappointment, there’s a small element of relief. Survivor is a form of self-inflicted torture that probably subtracts years from one’s life. Every time Rhamondre Stevenson broke the initial tackle yesterday was like someone tightening a vice around my internal organs. There was nothing I could do but watch, and I even thought about turning it off. At one point, I was so enraged, I had to calm down consciously and refuse to get further embittered by events going against me. Mike Gesicki had a TD catch overturned because he didn’t hold the ball to the ground, The next play Tanner Hudson fumbled while running unimpeded to the end zone. I kept posting, “Don’t tilt” after every negative play.
There’s a perverse enjoyment to getting enraged about what’s going on, out of your control, on a TV screen, but when you examine the experience, it really isn’t good or wholesome. I become like a spoiled child, ungrateful for everything, miserable and indignant at myriad injustices and wrongs I’m powerless to prevent.
At one point Sasha came in to tell me she had downloaded some random game from the app store on her Raspberry Pi computer. I had no interest in this as I was living and dying with every play, but I had forced myself to calm down so much already, I actually went into her room to check it out, not a trace of annoyance in my voice or demeanor.
I don’t think she cared about the game, or about showing it to me, but had stayed with her friends most of the weekend and was just using it as an excuse to spend a moment together with her dad. I scratched her back for a couple seconds while standing behind her desk chair. The game was still going on, and even though I was probably going to lose, and I was still sick about it, I was glad to have diverted a moment’s attention from it to Sasha.
. . .
In last week’s Survivor post, I wrote:
What method do I propose to see into the future? Only my imagination. I’m going to spend a lot of time imagining what might happen, turn my brain into a quantum device, break space-time and come to the right answers. Easier said than done, but I’m committed.
It’s possible I did this, but simply retrieved my information from the wrong branch of the multiverse. It happens.
. . .
I picked the Bengals knowing full well the Bills were the correct “pot odds” play which is my usual method. Maybe when the pot-odds are close, I might go with my gut, but they were not especially close this week, and yet I still stuck with Cincinnati because they were the team I trusted more.
And despite it being a bad pick — there are no excuses in Survivor, no matter what happens in the game, if you win it’s good, and lose it’s bad — I don’t feel that badly about it.
I regret it only because I wish I were still alive, but it was my error. I went with what I believed, and it was wrong. That I can live with 100 times better than swapping out my belief for someone else’s and losing. Had I done that I’d be inconsolable.
. . .
I won’t let the Survivor debacle undermine my real mission to bring sports to nostr. Team of Destiny 2 would have been a compelling story, but it was never essential. After all, my flight was cancelled and I had to improvise, so now my Survivor entry is cancelled, and I’ll have to improvise again. The branch of the multiverse where the Bengals won didn’t give me the information I wanted, but maybe it was what I really needed to know. That I am the man in the arena yet, the battle was ever against myself, and for a brief moment, while my team was losing, I prevailed.
-
 @ d3052ca3:d84a170e
2024-09-09 15:43:38
@ d3052ca3:d84a170e
2024-09-09 15:43:38I bought this for my son but it's a little advanced for his skills. Well, somebody has to find the princess and save Hyrule, right? Looks like it's gotta be me. :)
I have found the climbing, skydiving, and barbarian armor sets most useful. What other items can I unlock that will enhance my play experience? I just found the gloom resistance helmet but haven't tried it out yet.
What is the deal with horses? I tamed and boarded two so far but I haven't found an actual use for them yet except one korok hidden under a drain plug that I needed a horse to unplug. You don't need them for travel. They can't climb steep slopes or cross water so it's just easier and faster to skydive close to your destination and cover the last miles on foot. Do mounts serve a purpose or just look cool and help you get a few korok seeds?
What is your experience? I'd love to hear about it!
-
 @ ff6187a2:ddbe1be7
2024-10-24 12:54:45
@ ff6187a2:ddbe1be7
2024-10-24 12:54:45Happy Halloween
-
 @ 9e69e420:d12360c2
2024-10-24 11:51:32
@ 9e69e420:d12360c2
2024-10-24 11:51:32Dr. Johanna Olson-Kennedy, a leading advocate for trans youth care, withheld a $10 million study funded by taxpayers on the effects of puberty blockers, which found no improvement in mental health among participants.
She feared the findings would be "weaponized" against transgender care. Critics argue that her decision violates research standards and denies vital information to the public. The study tracked 95 children, revealing that 25% had mental health issues prior to treatment, contradicting Olson-Kennedy's claims of good overall mental health. Experts stress the importance of publishing research regardless of outcomes.
Sauce: https://nypost.com/2024/10/23/us-news/doctor-refused-to-publish-trans-kids-study-that-showed-puberty-blockers-didnt-help-mental-health/
-
 @ e968e50b:db2a803a
2024-09-09 13:22:12
@ e968e50b:db2a803a
2024-09-09 13:22:12I just wanted to let y'all know that I added a more sports themed UI option for the crossword puzzle from last week. You can get to it like so:
Also, there's still an unclaimed bounty for anybody interested in solving the additional puzzle.
originally posted at https://stacker.news/items/678010
-
 @ 45bda953:bc1e518e
2024-10-24 11:31:16
@ 45bda953:bc1e518e
2024-10-24 11:31:16Revelation Chapter 2:17
“He who has an ear, let him hear what the Spirit says to the churches. To him who overcomes I will give some of the hidden manna to eat. And I will give him a white stone, and on the stone a new name written which no one knows except him who receives it.”
Revelations is a mysterious book with some verses that seems to make very little sense.
Q: Why do we need names? A: To identify ourselves.
Same reason nature opted for us to have uniquely identifiable faces. But a name no one knows except him who receives it? Why would you need that?
When you are born you have very little in the way of personality and character. Doctor exclaims, “It’s a boy!” First verifiable identifier is recognised. One newborn baby looks very similar to another. For that reason they can accidentally be mixed up and given to the wrong mother at the hospital. But if the mother knows that she birthed a boy she would immediately know something is amiss if she gets handed a newborn girl. Gender is important as the first verifiable, unique identifier of the new being.
The newly confirmed male child gets issued a verbally spoken and symbolically scripted identifier. This identifier is known as a name. Name and surname please. These identifiers are of little consequence to the being who knows only feelings of pain and sensations of comfort. The survival of the biological spawn is dependant on the instinct to suckle and the tendency to cry at slight discomfort. This is the language of human instinct to cry and suck. As the toddler develops it starts to respond to the vocally repeated identifier (known as a name) to the point where it has been sufficiently trained to respond to the verbal enunciation of it. When you call for someone you are evoking hope that the entity being called to will respond by coming to your physical location so that you can share or enquire information. When the summons is answered by presence you maintain connection not by repetition of the name but by eye contact and directing conversation to the face of the person. The face being the most accurate point with which to verifiably establish identity.
In the book of Genesis Jacob is able to fool Isaac (His father) by exploiting his bad eyesight to steal an inheritance blessing from his older brother Esau. The face of Jacob was obscured through Isaac’s blindness which gave a false signal to the issuer of a blessing.
As our proverbial John Doe grows up he develops a personality and character which allows for people to gauge the levels of trust they are willing to risk on him. Character and personality are also unique identifiers. Mother knows best at who will be diligent when keeping their rooms clean and whose rooms she will have to clean for them. She can through experience predict outcomes using knowledge of character and personality as a reference. This information is valuable and can only be established or measured when there is an ongoing relationship where trust and responsibility are continuously tested and stressed.
We all have identifiers that are publicly displayed wherever we go.
: Physical appearance, Wedding ring, Tatoo
We have identifiers that represent or address us verbally and textually.
: Names, titles, seals, signatures, handwriting et cetera.
Ambiguous identifiers
: Left handed, smoker, married, divorced, affiliations, church, political views, phone number, address, favourite colour, drivers license ad infinitum.
In this digital world our identifiers are all exploitable by a large number of unidentifiable bad actors. This is weakness. If you are a man of character and strength but have no control over your identity. You are weak and defenceless in the eyes of these virtually indistinguishable, androgynous scammers, fraudsters, monopolies and governments.
We have to take digital sovereignty over our digital identities. That means we have to train our minds in the establishment of truth. The truth being...
Be true to thine self and let the truth about you be established by you. That means abandoning trust in third parties and know that no one is coming to save you and protect your personal data. Like there is no spoon in the matrix, there is also no institution who loves you enough to protect your identity in a digitally encrypted world. In some cases they might be legally obligated to, but who will take responsibility and how do you quantify and reverse the damage of leaked information. You don’t. No justice for the slave.
The spoon is a lie. It simply does not exist.
Revelation Chapter 2 verse 17
“He who has an ear, let him hear what the Spirit says to the churches. To him who overcomes I will give some of the hidden manna to eat. And I will give him a white stone, and on the stone a new name written which no one knows except him who receives it.”
 If you have an identifier that only you know about then you have a private key. You can verify your holdings of assets. You can prove your identity on nostr. You can own not only the data but prove you are the source of it.
If you have an identifier that only you know about then you have a private key. You can verify your holdings of assets. You can prove your identity on nostr. You can own not only the data but prove you are the source of it.Anything that a trusted third party is currently doing for you, analog or digital is systemically being open sourced and you could do it for yourself with the press of a button. All you need is a white stone with a name on it no one else knows and be willing to carry the responsibility. You could then selectively reveal yourself to the world and prove it is you without exposing the you that is private. I will give an example to help you understand the power.
John 19:31–42
31 Therefore, because it was the Preparation Day, that the bodies should not remain on the cross on the Sabbath (for that Sabbath was a high day), the Jews asked Pilate that their legs might be broken, and that they might be taken away. 32 Then the soldiers came and broke the legs of the first and of the other who was crucified with Him. 33 But when they came to Jesus and saw that He was already dead, they did not break His legs. 34 But one of the soldiers pierced His side with a spear, and immediately blood and water came out.
One thing is certain, Jesus was verifiably dead. The Romans, Jews and disciples who were present at the execution and burial all concurred. He is dead. Deceased. Gone from the realm of the living. Roman soldiers were veritable experts at death and declaring the dead so.
A few days later some disciples were proclaiming excitedly about Jesus being alive. A certain guy named Thomas would not be had. You guys are crazy, trying to establish some weird cult by pretending a fantastic impossibility. Nope. They were adamant. He lives. They claimed, like a bunch of fanatics. Thomas, being the voice of reason says the following.
John 21:25
25 The other disciples therefore said to him, “We have seen the Lord.” So he said to them, “Unless I see in His hands the print of the nails, and put my finger into the print of the nails, and put my hand into his side, I will not believe.”
Thomas was a real Bitcoiner. He does not trust, he verifies.
 Verification in progress.
Verification in progress.The body of Jesus, should he have been alive will have been littered with scar tissue all across his back and legs. It would have been easy for Him to selectively reveal his identity to whoever he chose by exposing his body and letting them verify the proof of his identity without doubt. No one in world history has ever committed suicide by flogging and crucifixion so you cannot even fake or repeat it if you wanted to commit identity theft and pretend to be the Christ.
A proof of work hash in history so profound that civilisations collapsed on the realisation of its profundity. Another consequential exposition of identity verification is also expounded on by the gospel accounts.
Matthew 24:5
“For many will come in My name, saying, ‘I am the Christ,’ and will deceive many.
Eric Cason on the "What Bitcoin Did" podcast said that he thinks Bitcoin is a messianic event. I agree with him. Liberation from economic tyranny is messianic if a figure initiates the salvation process.
That would suggest that there will be messianic implications, namely identity fraud of messiah with the intent to deceive and extort.
Matthew 24:23
23 “Then if anyone says to you, ‘Look, here is the Christ!’ or ‘There!’ Do not believe it.
We have ourselves an example of this in Craig Wright who claims to be Satoshi Nakamoto. Yet he refuses to verify it by transferring Genesis bits. Like Thomas demands to see the scars of crucifixion so too must we demand to see on chain movement of Genesis coinbase block reward as proof of identity and proof of work from anyone who publicly makes a claim to the person of Satoshi Nakamoto. Historic records in the future might mark this dispensation, BWP (Before white paper) and ASN (After Satoshi Nakamoto) or something of this nature could stand in the annals of history, marking a era of mankind similar to BC, Before Christ and AD, anno domini, the year of our Lord.
Jesus is yet to give me a secret name like Satoshi already did.
Which leaves me wondering…
 The simulacral spectre created by Satoshi is an ongoing rabbit hole,
The simulacral spectre created by Satoshi is an ongoing rabbit hole,I have no doubt.
...
bitbib
-
 @ 8dc86882:9dc4ba5e
2024-09-08 22:14:05
@ 8dc86882:9dc4ba5e
2024-09-08 22:14:05Why do lightning nodes need channels? Why can a node not just send and receive without a channel? I wonder what the benefit it serves other than making running a node difficult or making it cost to open one?
Thanks
originally posted at https://stacker.news/items/677439
-
 @ c0f9e286:5a223917
2024-10-24 09:37:21
@ c0f9e286:5a223917
2024-10-24 09:37:21ตอนที่แล้วได้กล่าวถึงการตั้งบริษัท Holding Company เพื่อนำมาถือหุ้นในบริษัทลูก จุดประสงค์นอกจากจะเป็นการประหยัดภาษีแล้ว ยังง่ายต่อการควบคุม เนื่องจากแบ่งสัดส่วนการถือหุ้นกันตั้งแต่ต้น ซึ่งหากถือในนามบุคคลธรรมดาย่อมปกปิดตัวตนที่แท้จริงไม่ได้ ดังนั้นหลายๆบริษัทจึงนิยมตั้ง Offshore Holding (Holding ที่ตั้งในต่างประเทศ) เข้ามาถือหุ้นบริษัท Holding ในประเทศอีกทีหนึ่ง
นั่นแปลว่าวุ่นวายกับการตั้งบริษัท Offshore Holding แค่ครั้งเดียว หลังจากนั้นก็นำมาถือหุ้นใน Holding ในประเทศเพื่อเป็นเจ้าของทุกๆบริษัทในเครือ ซึ่งมีอำนาจควบคุม บังคับบัญชา และสั่งการโดยไม่จำเป็นต้องเปิดเผยตัวตนที่แท้จริง
ส่วนถ้าจะถามว่าไปตั้ง Offshore ประเทศไหนดี อันนี้ขึ้นกับวัตถุประสงค์ของแต่ละท่าน ซึ่งไม่มี One Size fits all บางคนตั้ง Offshore มาเพื่อรับเงินก้อนใหญ่จากการขายหุ้น และไม่ได้ต้องการปกปิดตัวตนอะไรมากมายก็อาจจะไปตั้ง Offshore ที่ Hong Kong หรือ Singapore
แต่ถ้าวัตถุประสงค์ต้องการที่จะปกปิดตัวตน อาจจะไปตั้งในประเทศอย่าง Seychells, Vanuatu, Mauritius หรือ BVI เป็นต้น ซึ่งประเทศเหล่านี้มักมีนโยบายไม่เปิดเผยตัวตนของบุคคลที่เป็นเจ้าของหุ้นในบริษัท และที่สำคัญ ประเทศเหล่านี้บางทียอมให้นิติบุคคลต่างประเทศเข้ามาเป็นผู้ถือหุ้นได้ 100% (กฎหมายไทยในการตั้งบริษัทต้องมีผู้ถือหุ้น 2 คนขึ้นไป และหากไม่มีโรงงานในไทย หรือได้รับสิทธิ BOI ต่างชาติสามารถถือหุ้นได้ไม่เกิน 49%)
ดังนั้นหาก Offshore Company 1 ชั้นยังไม่พอ คุณก็ตั้ง Offshore ไปเลย 2 ประเทศเช่น ผมอาจจะตั้ง Offshore แรกที่ Vanuatu ซึ่งผมถือหุ้น 100% (ในนามบุคคล) แล้วจึงไปก่อตั้งอีก 1 บริษัทอีกแห่งที่ Seychells โดยให้ Vanuatu Offshore เข้าไปถือหุ้น 100% ในนามบริษัท แล้วผมจะนำ Seychells Offshore มาถือหุ้นใน Thailand Holding อีกทีหนึ่ง ซึ่งหาก Thailand Holding ไม่ได้มีโรงงาน หรือได้รับสิทธิ BOI แปลว่า Seychells Offshore จะเข้าไปถือหุ้นได้ไม่เกิน 49% ส่วนอีก 51% คุณควรหานอมินี หรือคนในครอบครัวที่ไม่ได้กังวลเรื่องความเป็นส่วนตัวเข้ามาถือหุ้นแทน และอาจจะจำกัดสิทธิออกเสียงผ่านกลไกการถือหุ้นบุริมสิทธิ์แทน เอาเป็นว่าเดี๋ยวจะงง แต่ให้เข้าใจไว้ว่า 51% ที่ถือหุ้นแทนมีช่องทางที่ทำให้เสียง Vote หรือสิทธิในการรับเงินปันผลน้อยกว่าฝั่ง 49% ซึ่งเดี๋ยวจะหาเวลาอธิบายเรื่องนี้โดยละเอียดอีกครั้งหนึ่ง
แปลว่าหากทางรัฐบาลไทยตรวจสอบรายชื่อผู้ถือหุ้นหรือทรัพย์สินของคุณ หากใช้การถือทรัพย์สินแบบนี้ย่อมไม่มีทางที่รัฐจะรู้เลยว่าคุณเป็นเจ้าของทรัพย์สิน หรือกิจการอะไรกันแน่ และหากรัฐบาลไทยต้องการตรวจสอบจริงๆ การจะไปตรวจพิสูจน์ว่าใครถือหุ้น หรือมีสิทธิในการครอบงำบริษัทจะเป็นเรื่องยากมาก
ซึ่งหากคุณคิดว่านี่ยังเป็นส่วนตัวไม่พอละก็… แน่นอนมีวิธีที่จะเพิ่มความเป็นส่วนตัวมากขึ้นกว่าเดิม ซึ่งมีอีก 2 วิธี และสามารถนำมาใช้ร่วมกับวิธีนี้ได้ ส่วนจะเป็นวิธีอะไรนั้น รอติดตามตอนต่อไป
Own Nothing and be Happy ในแบบฉบับ Elite เป็นไงบ้างครับ เริ่มเห็นภาพหรือยังว่าทำไมตระกูลดังๆอย่าง Rothschild สามารถปกป้องความเป็นส่วนตัวของพวกเขาไว้ได้โดยที่คนนอกไม่รู้เลย ก็เพราะเครื่องมือแบบนี้ไง
realeakkrit #siamstr #privacy
-
 @ a828c9af:ea95c44c
2024-10-24 08:25:30
@ a828c9af:ea95c44c
2024-10-24 08:25:30The Philippines is a goldmine for businesses seeking new markets. With a booming economy and a population exceeding 100 million, it presents a vibrant and diverse consumer landscape that, when maximized, can offer businesses a considerable market with a growing purchasing power.
Moreover, the country's e-commerce sector has exploded in recent years, with sales hitting $17 billion in 2021 alone. As consumer behavior rapidly evolves due to technology and changing preferences, there's never been a better time to enter the Philippine market than today.
5 Ways to Tap into the Philippine Market
To succeed in the Philippine market, you need a strategic approach that resonates with the country's diverse and dynamic consumer base. Here are five proven methods to help you engage effectively.
1. Digital services and marketing
In the Philippines, a solid online presence is crucial to reach your target audience. Use social media, content marketing, and search engines to build meaningful connections almost instantly.
2. Cashless and online payment methods
Filipino consumers prefer secure and convenient payment options. Offering various cashless and online payment methods can enhance their shopping experience and give your business a competitive edge.
3. Fashion eCommerce
Fashion eCommerce is booming in the Philippines. A visually appealing website with high-quality images, detailed product descriptions, and easy navigation can attract fashion-conscious Filipinos.
4. Localized content and engagement
Tailor your content to your customers' culture and values to connect with the Philippine market. Using the local language, cultural references, and relatable imagery can deepen customer engagement and build trust.
5. Responsive customer support
Excellent customer support builds trust and loyalty. When you offer timely, helpful responses through chatbots and automation while maintaining a personal touch ensures customer satisfaction.
Check this infographic to learn more about consumer trends in the Philippines and how to take advantage of them to tap into this lucrative market.
-
 @ eed76ece:afa98124
2024-09-08 21:13:37
@ eed76ece:afa98124
2024-09-08 21:13:37Seems like if you want to sell an item on SN using @AGORA makes logical sense.
Perhaps if your a manufacturer, importer, exporter, stocking distributor, wholesaler etc. you should also consider using @Import_Export or both @AGORA and see if they help each other. Being totally upfront Import_Export is probably a better use case especially if you are running over 75% B2B.
We are note promoting the use of B2C on SN. We're 100% focused on interactions between businesses only. Our primary markets are in Asia and Southeast Asia. Europe and the UK are dying a slow death, and the last straw was the Telegram event.
So I am endorsing you to please at least on SN refer to @AGORA for basic B2C (retail).
Thank you, https://www.globalmerchant.io
originally posted at https://stacker.news/items/677390
-
 @ e8b86bc1:3503c58f
2024-09-08 19:37:36
@ e8b86bc1:3503c58f
2024-09-08 19:37:36Opinion about Freewallet Multi Crypto Wallet (iphone)
Freewallet is now charging inactivity fees, a sneaky method to take money from users who aren’t regularly using the app. Avoid this scam wallet!
WalletScrutiny #nostrOpinion
-
 @ c11cf5f8:4928464d
2024-09-08 19:10:39
@ c11cf5f8:4928464d
2024-09-08 19:10:39Considering the "whatever" item in question is a random item, a unique piece --not something you produce or need to market-- which platform, website or which strategy you'll put in place to get the value of your item in sats, immediately, anonymously, via the Lightning Network?
originally posted at https://stacker.news/items/677270
-
 @ 6f170f27:711e26dd
2024-09-08 17:45:46
@ 6f170f27:711e26dd
2024-09-08 17:45:46Far too many people: "GDP is bad. I prefer [thing correlated at 0.9 with GDP]."
Manufacturing:
Life expectancy:
Happiness:
Many other metrics & discussion in the source:
https://x.com/cremieuxrecueil/status/1832588128084730334
originally posted at https://stacker.news/items/677211
-
 @ 97fc03df:8bf891df
2024-10-24 07:53:50
@ 97fc03df:8bf891df
2024-10-24 07:53:50A Value Internet Sharing Bitcoin’s Consensus Security
Author: BEVM, October 2024
Abstract
Super Bitcoin is a value-based internet centered on BTC, and share Bitcoin's consensus security. This value internet not only inherits the security of the existing Bitcoin network but also transcends BTC's current limitations of being solely used for transfer, providing the Bitcoin network infinite potential for scalability and flexibility.
While the Lightning Network [2] inherits Bitcoin's network security and offers partial scalability solutions, it still falls short in supporting smart contracts and further enhancing scalability. We propose a five-layer architecture for Super Bitcoin using the Bitcoin network as the kernel layer, maintaining system security and transaction irreversibility through the proof-of-work (PoW) consensus mechanism; we build an efficient communication layer based on the Lightning Network, facilitating rapid transmission of asset information while preserving Bitcoin's decentralized nature; we introduce the Taproot Consensus as the extension layer, abstracting Lightning Network communication and asset information to provide a standardized interface for the upper virtual machine layer; we set up a multi-chain layer, also known as the fusion layer, which consists of multiple lightning chains secured by BTC consensus, integrating any mainstream virtual machine (VM) to achieve a "Multi-chain interconnection“ and ”multi-chain interoperability” unified by BTC consensus; finally, we support the application layer, providing developers with rich tools and interfaces to build a decentralized application (DApp) ecosystem, all sharing the security of BTC consensus.
1. Introduction
As the pioneer of cryptocurrencies, Bitcoin (BTC), through its proof-of-work (PoW) consensus mechanism and decentralized network structure, has garnered an immense level of consensus, becoming a supranational currency. This security stems from the perfect combination of its vast network hash power and economic incentives. The birth of Bitcoin not only ushered in a new era of decentralized digital currency but also pointed the way for the subsequent development of blockchain technology. However, the limitations of Bitcoin’s scripting language soon became apparent, as it only supports simple value transfers and limited contract logic, unable to meet the demands of more complex decentralized applications.
The evolution of blockchain technology is essentially all about expanding and enhancing Bitcoin's capabilities. Vitalik Buterin, the founder of Ethereum, initially envisioned adding smart contract functionality to Bitcoin. However, due to the technological constraints of the time and the limitations of the Bitcoin network, Ethereum had to establish its own independent consensus system. While this approach allowed for the creation of Turing-complete smart contracts, it also introduced new security risks and scalability challenges. Many projects followed suit, building independent blockchain ecosystems, gradually diverging from and even forgetting the original intention of extending Bitcoin’s capabilities.
However, two key factors remind us of the need to reconsider this direction. First, the continued rise in Bitcoin’s value relative to other cryptocurrencies like Ethereum has validated the trust people place in its security and stability. Second, the collapse of Luna/UST, which wiped out nearly $100 billion in market value, highlighted the severe security vulnerabilities present in independent consensus chains, especially when faced with complex economic models and rapidly growing network value.
In this context, we introduce Super Bitcoin to create a true value internet sharing Bitcoin's consensus security. It fundamentally differs from the existing Bitcoin Layer 2 solutions: traditional Bitcoin Layer 2 solutions (such as the Lightning Network) mainly achieve fast payments through off-chain state channels and limited scripts, while sharing Bitcoin's consensus security but lacking flexibility. Meanwhile, sidechains like Stacks or Layer 2 solutions, although they support smart contracts, still rely on independent multi-signature mechanisms for security, thus not fully inheriting the security of the Bitcoin mainnet.
2. Technical Background
To fully understand the proposed solution, it is necessary to first review the background and development of several key technologies. This chapter briefly introduces the Lightning Network, the Substrate framework [3], BEVM's Taproot Consensus, and the multi-chain interoperability system to provide a foundation for understanding our solution.
2.1 Lightning Network
The Lightning Network is a Layer2 scaling solution for Bitcoin, with its core design principles detailed in the BOLT (Basis of Lightning Technology) specifications. These specifications not only ensure the efficient operation of the Lightning Network but also ingeniously achieve deep integration with the consensus security of the Bitcoin mainnet. Several parts of the BOLT specifications play a key role in sharing Bitcoin’s consensus security.
BOLT #2 and BOLT #3 provide detailed guidelines on the lifecycle management of payment channels and the structure of transactions. The opening of a channel involves creating a multi-signature output on the Bitcoin blockchain, while closing the channel requires broadcasting the final state to the mainnet. BOLT #3 specifically defines commitment transactions, which are the core mechanism by which the Lightning Network shares Bitcoin's consensus security. Each time the channel state is updated, a new commitment transaction is generated, which can be broadcast to the Bitcoin mainnet if needed. The design of commitment transactions ensures that even if one party in the channel becomes uncooperative, the other party can still close the channel by broadcasting the most recent commitment transaction and receive their due funds. This mechanism directly relies on Bitcoin’s consensus rules and security, meaning the Lightning Network’s security is essentially guaranteed by the Bitcoin network.
BOLT #5 defines the penalty mechanism for channel closures. This mechanism introduces the concept of "revocating private keys," effectively preventing participants from broadcasting outdated channel states. If dishonest behavior is detected, the honest party can use these keys to punish the other party on the Bitcoin main chain, thereby ensuring the accuracy of the channel state and enforcing honest behavior among participants through Bitcoin's consensus mechanism.
Additionally, the commitment transaction format specified in BOLT #3 connects Lightning Network transactions to Bitcoin's fee market through "anchor outputs." This not only enhances the security of transactions but also ensures that Lightning Network transactions can still be confirmed promptly during periods of network congestion.
These meticulously designed specifications collectively ensure that the Lightning Network, while providing fast and low-cost transactions, can still fully leverage Bitcoin's robust consensus security.
2.2 Substrate Framework
The Substrate framework is a highly modular blockchain development toolkit written in Rust, providing a powerful and flexible technical foundation for the implementation of Super Bitcoin. Its core strength lies in its pluggable Pallet system, where these pre-built functional modules serve as "blockchain Legos," enabling us to quickly and efficiently assemble and customize the desired features.
For Super Bitcoin, Substrate's modular design is crucial. It allows us to flexibly build and integrate various functional components on top of the shared Bitcoin consensus security. By leveraging Substrate's Pallet, we can easily support and integrate different virtual machine environments, thereby increasing the system's flexibility and adaptability. This design not only accelerates the development process but also provides Super Bitcoin with powerful scalability, allowing it to better meet the evolving needs of the blockchain ecosystem.
Super Bitcoin utilizes these features of Substrate to customize the BEVM-stack framework, which enables one-click deployment of lightning chains.
2.3 Taproot Consensus
BEVM’s Taproot Consensus integrates Bitcoin’s Taproot upgrade [4] technology. This technology combines several key elements: Schnorr signatures [5] provide signature aggregation capabilities, Merkelized Abstract Syntax Tree (MAST) support complex conditional scripts, and Musig2 enables two-round communication in multi-signature schemes. Through the combination of these technologies, BEVM successfully implements a decentralized threshold signature network with (t, n) support.
Additionally, BEVM leverages Bitcoin SPV (Simplified Payment Verification) technology to achieve lightweight decentralized block header synchronization. This allows transaction verification without downloading the full blockchain data, enabling BEVM to synchronize with the BTC mainnet in a decentralized manner. In Super Bitcoin architecture, Taproot Consensus plays a key role as the extension layer: it interfaces with the Lightning Network below, abstracting and integrating asset information, and provides standardized interfaces for different virtual machine execution environments above, realizing the transmission and utilization of asset information.
Such design makes Taproot Consensus a core component of the Super Bitcoin architecture. It not only inherits the security and privacy-preserving characteristics of the Bitcoin network but also provides rich functional support for upper-layer applications.
2.4 Multi-Chain Interoperability System
The concept of a multi-chain interoperability system was first introduced by Polkadot. Polkadot [6] is a multi-chain interoperability system based on the Substrate framework, sharing the security of DOT consensus, and using parachains for application chain expansion. Correspondingly, Super Bitcoin is a multi-chain interoperability system built on Bitcoin and the Lightning Network, sharing BTC consensus security, and using Lightning Chains for application chain expansion.
The differences between the two are as follows:
-
Shared Consensus Security: Both Polkadot and Super Bitcoin’s multi-chain networks achieve shared consensus security, but Polkadot shares DOT consensus, while Super Bitcoin shares Bitcoin consensus. The strength of BTC’s consensus is far greater than that of DOT. Theoretically, the security of the Super Bitcoin architecture is 200 times higher than that of the Polkadot network. This "200 times" represents the current ratio of BTC’s $1.3 trillion market cap to DOT’s $6.5 billion market cap. Therefore, the Lightning Chains on Super Bitcoin offer approximately 200 times the security of Polkadot's parachains.
-
Application Chain Architecture: Super Bitcoin’s lightning chain is deployed with one click based on BEVM-stack, whereas on Polkadot, parachains are deployed via Substrate with one-click.
-
Cross-Chain Communication Protocol: Super Bitcoin uses lightning channels as the communication protocol between Lightning Chains, while Polkadot uses XCMP as the communication protocol between parachains.
3. System Architecture

3.1 System Architecture Overview
Super Bitcoin is a five-layer architecture protocol built by BEVM guided by the three problems of blockchain - decentralization, security and scalability.. This protocol is based on the Bitcoin protocol and utilizes the Lightning Network for efficient peer-to-peer communication. To extend the functionality of Lightning Network nodes, Super Bitcoin integrates Taproot Consensus and combines Bitcoin SPV, Schnorr signatures, MAST contracts, and a BFT PoS consensus mechanism to achieve scalable state management and transaction processing.
On this foundation, Super Bitcoin further integrates multiple virtual machines, including WASM, EVM, SVM, MoveVM, and CairoVM, creating a multi-chain system based on lightning chains that offers a diverse range of smart contract execution environments. This modular framework significantly enhances the system's scalability and flexibility while maintaining the decentralized nature of the Bitcoin network. Importantly, all lightning chains share the Bitcoin network's consensus security, ensuring that the system remains highly secure as it scales.
3.2 Kernel Layer
The Bitcoin network serves as the kernel layer of Super Bitcoin, maintaining the security and irreversibility of the entire system through the Proof-of-Work (PoW) consensus mechanism. This decentralized peer-to-peer electronic cash system primarily supports BTC transfers and basic opcode execution, managing state using the UTXO model. The Bitcoin network’s block structure and transaction data serve as the input for the Lightning Network, providing reliable foundational data for the upper layers. Although Bitcoin’s scripting system is not Turing-complete, it can support the most basic smart contract functionality through stack-based operations, conditional checks, and cryptographic functions. The network maintains a block time of approximately 10 minutes using a difficulty adjustment algorithm and uses Merkle tree structures to optimize transaction verification efficiency. The security and decentralization of this foundational layer provide a robust consensus security foundation for the entire Super Bitcoin architecture, while its simple design and limited scripting capabilities offer a stable and predictable environment for upper-layer expansion.
3.3 Communication Layer
The Lightning Network serves as the communication layer of Super Bitcoin, achieving efficient asset information transmission while sharing the BTC consensus security. It acts as a bridge between users and the Super Bitcoin ecosystem, enabling bidirectional payment channels through a Hashed Time Lock Contract (HTLC), supporting multi-hop routing and atomic swaps. Users can establish state channels with Super Bitcoin nodes to deposit funds and conduct instant off-chain transactions.
Super Bitcoin nodes, as specialized Lightning Network nodes, not only maintain direct channels with users but also remain compatible with the existing Lightning Network by implementing the BOLT (Basis of Lightning Technology) specifications. This design allows users to leverage the existing Lightning Network infrastructure for cross-node, cross-chain payments and value transfers, providing a secure communication foundation for the lightning chains.
3.4 Extension Layer
Taproot Consensus serves as the extension layer in Super Bitcoin, playing a critical role in connecting the Lightning Network with the upper-layer lightning chains. It abstracts the asset information transmitted through the Lightning Network and converts it into blockchain data that can be processed by the upper layers, balancing the payment efficiency of the Lightning Network with the logical needs of upper-layer applications.
This expansion layer integrates Bitcoin SPV, Schnorr signatures, MAST (Merkelized Abstract Syntax Tree) structures, and a BFT (Byzantine Fault Tolerance) PoS consensus mechanism to achieve multiple functions:
1. Connecting the Lower Layer :Bitcoin SPV enables lightweight block header verification, allowing nodes to synchronize with the Bitcoin network in a decentralized manner, providing reliable on-chain data input for the Lightning Network.
2. Information Processing and Storage: The PoS-based blockchain network provides distributed storage of Lightning Network channel states. It also processes information for BTC and Taproot Assets, supplying necessary data for upper-layer applications. This mechanism ensures data redundancy and resistance to censorship.
3. Security Assurance : Decentralized threshold signatures replace the local key management system of Lightning Network nodes, enhancing key security and flexibility. The aggregation feature of Schnorr Signatures is used to construct a (t, n) threshold signature network, replacing the traditional single-key management model of the Lightning Network.
4. Privacy and Complexity : The MAST structure allows complex conditional scripts to be represented on-chain as a single hash, improving both privacy and script complexity. Through these mechanisms, the Taproot Consensus extension layer effectively converts verified Lightning Network data into standardized blockchain states. While ensuring security and privacy, it enhances the overall system's performance and scalability. It not only connects the underlying Bitcoin and Lightning Networks but also provides the upper-layer applications with rich and reliable data and functional support.
#### 3.5 Fusion Layer The Fusion Layer reflects the scalability of Super Bitcoin. It builds on top of Taproot Consensus and utilizes the extensibility of the Substrate framework to achieve a multi-chain interconnected system. Its key features include:
1. Scalable Multi-Chain Architecture: Supports the deployment and interconnection of an unlimited number of lightning chains, with BEVM serving as a special lightning chain responsible for managing cross-chain interactions and resource scheduling.
2. Heterogeneous Compatibility and Standardized Protocols: Compatible with multiple virtual machines (such as MoveVM, CairoVM, SVM, EVM) and achieves atomic asset exchange and state synchronization through a standardized cross-chain protocol based on the Lightning Network.
3. Shared Security and Flexible Consensus: All lightning chains inherit the security of the Bitcoin network, while adopting a pluggable consensus design, with the default being a Taproot-compatible BFT variant.
4. Ecosystem Expansion: Facilitates the rapid migration of existing blockchain technologies, extending the decentralized BTC ecosystem to various Turing-complete blockchain applications.
With these features, the Fusion Layer enables Super Bitcoin to evolve into a highly scalable, secure, and interoperable multi-chain ecosystem, providing robust infrastructure support for blockchain innovation.
3.6 Application Layer
The Application Layer is built on top of Super Bitcoin's multi-chain architecture, offering developers a diverse decentralized application (DApp) ecosystem. Leveraging the security, scalability, and interoperability of the underlying layers, it supports the deployment of applications on any Turing-complete virtual machine. Developers can choose to quickly deploy proprietary application chains within the lightning chain framework, or they can deploy various applications directly on the lightning chains. All these applications and chains automatically inherit the consensus and security guarantees of the Bitcoin network.
The Application Layer integrates multiple smart contract execution environments, supporting programming languages such as Solidity (EVM), Move, Cairo, and Rust. The Application Layer lowers the entry barrier for developers and accelerates the innovation cycle. Through standardized API interfaces, developers can utilize Lightning Network channels to achieve decentralized cross-chain asset transfers and information exchanges. Additionally, it incorporates protocols like Taproot Assets, which are compatible with the Lightning Network, further enhancing cross-chain functionality.
Although the services provided by the Application Layer are similar to other VM-based public blockchains, it has two distinctive features: first, it allows the use of decentralized native BTC as the base currency for applications; second, the entire application layer shares the security of the Bitcoin network. Such design not only offers a rich development environment but also ensures that applications are built on solid security and native cryptocurrency support.
4. Shared Consensus Security
Shared BTC consensus security is the security core of our five-layer architecture. This concept is derived from Polkadot's shared security model, which Polkadot defines as Shared Security, also known as Pooled Security, is one of Polkadot's unique value propositions. In essence, it means that all parachains connected to Polkadot's relay chain benefit from the full security of the entire Polkadot network.
Our five-layer protocol architecture further extends this concept by leveraging the Bitcoin (BTC) network—currently recognized as the most secure blockchain consensus system—to ensure the security of the entire ecosystem. Compared to Polkadot's parachains, which share Polkadot's consensus security, our architecture is directly built on top of the Bitcoin network, sharing Bitcoin’s consensus security.
Existing BTC Layer2 solutions typically ensure security through cross-chain mechanisms or BTC staking, which only utilize part of Bitcoin’s consensus security. In contrast, our five-layer protocol is built on the Lightning Network, using HTLC (Hashed Timelockd Contract) and commitment transactions, with security fully dependent on BTC consensus. This design allows our system to fully inherit the consensus security of the Bitcoin network.
Specifically, our architecture achieves shared BTC consensus security through the following methods:
-
Leveraging the peer-to-peer channels of the Lightning Network to ensure that all transactions are ultimately settled on the Bitcoin mainnet.
-
Using HTLC commitment transactions, where each state update is protected by the consensus of the Bitcoin network.
-
Through the Taproot Consensus extension layer, extending Bitcoin's security features to more complex smart contract environments.
-
In the multi-chain system, all lightning chains share Bitcoin’s network consensus security, ensuring consistency and reliability across the entire ecosystem.
5. Lightning Chain
Based on the shared BTC consensus security, we utilize the lightning chain to create a Value Internet. To achieve this, the architecture of the lightning chain network is inspired by Polkadot's relay chain and parachain design:
-
Relay Chain: It serves as the central nervous system of the entire network, responsible for the overall security, cross-chain communication, and consensus mechanism. The relay chain does not execute specific application logic but focuses on coordinating the operations of the entire ecosystem.
-
Parachains: These are independent blockchains that run in parallel with the relay chain. Each parachain can have its own token economy and governance mechanism, achieving interoperability through the relay chain and sharing the security guarantees provided by the relay chain. Drawing from Polkadot’s design, Super Bitcoin proposes a multi-chain interoperability system based on Bitcoin and the Lightning Network. In this system, the Lightning Chain functions similarly to Polkadot's parachains, with the following unique characteristics:
Shared BTC Consensus Security: Unlike Polkadot’s independent consensus model based on PoS staking, Lightning Chain directly inherits the consensus security of the Bitcoin network, providing unprecedented security for the entire ecosystem.
-
Lightning Network Integration: Lightning Chain deeply integrates Lightning Network technology, enabling high-speed, low-cost transaction processing, significantly enhancing the throughput and efficiency of the entire system.
-
Scalability: Theoretically, an unlimited number of Lightning Chains can be deployed, with each Lightning Chain optimized for specific application scenarios or industry needs, offering a high degree of flexibility and scalability.
-
BEVM as the Core Coordinator: In this ecosystem, BEVM (Bitcoin-Enhanced Virtual Machine) acts as a special Lightning Chain, playing a role similar to that of Polkadot’s relay chain. It is responsible for the governance and resource allocation of the entire network, ensuring efficient collaboration between different Lightning Chains.
-
Shared Lightning Network Liquidity: All Lightning Chains share the same Lightning Network, which means they can access a common liquidity pool, improving capital efficiency.
These features not only highlight the innovative design of Lightning Chain but also underscore its fundamental differences from existing BTC Layer 2 solutions. By directly sharing Bitcoin network consensus security and Lightning Network liquidity, Lightning Chain achieves a qualitative leap in both security and interoperability.
5.1 Lightning Chain
The Lightning Chain is the core component of Super Bitcoin that directly interacts with users. Its main responsibilities include handling user transactions, managing asset mapping, and executing smart contracts.
5.1.1 BTC Asset Mapping

Lightning Chain functions as both a node in the Lightning Network and a PoS (Proof of Stake) network. In this system, BTC is locked within the Lightning Network, while L-BTC represents the user's BTC balance in their Lightning Chain account. The mapping process between these two ensures the consistency and security of the assets. The specific BTC-to-L-BTC mapping process is as follows: - The user establishes a channel with the Lightning Chain via the standard Lightning Network protocol. - The user deposits A BTC into the Lightning Network channel. - As the Lightning Chain operates as a PoS network, the validators within the network observe this new BTC deposit. - Once more than two-thirds of the validators reach consensus and confirm the BTC deposit event, the Lightning Chain will issue A L-BTC accordingly.
This process ensures that the issuance of L-BTC always maintains a 1:1 ratio with the BTC locked in the Lightning Network channel. It's important to note that L-BTC is self-custodied by the user, so there is no need to worry about asset security. Additionally, PoS consensus here is not used to secure L-BTC assets but acts as a distributed ledger for the state of the Lightning Network channel, solving the potential issue of data loss in local storage by Lightning Network nodes.
5.1.2 Smart Contract Interaction on the Lightning Chain

Interaction with smart contracts on the Lightning Chain follows a "authorize first, execute later" paradigm. In this process, users need to convert L-BTC into M-BTC, where M-BTC represents the asset that can interact with smart contracts on the Lightning Chain. The specific interaction process is as follows:
- Asset Preparation: The user holds A BTC in the Lightning Network state channel and decides to interact with a smart contract using 1 BTC.
- Authorization Operation: The user authorizes the Lightning Chain network to convert 1 L-BTC into 1 M-BTC. This step does not immediately execute the conversion but provides the necessary permissions for subsequent interactions.
- Smart Contract Invocation: The user initiates a smart contract call, specifying the use of 1 M-BTC. The Lightning Chain network checks the authorization and, upon confirming its validity, performs the following actions: destroys 1 L-BTC from the user’s balance, mints 1 M-BTC, and uses it directly for interaction with the smart contract.
- Transaction Execution: The smart contract executes the specified operation using the minted M-BTC.
This process enables the seamless application of Bitcoin assets within a smart contract environment while maintaining a clear separation between L-BTC, which functions as channel liquidity, and M-BTC, which serves as a medium for contract interaction.
5.2 System Chain

System Chain is the core coordination component of Super Bitcoin implemented through the upgraded BEVM (Bitcoin-Enhanced Virtual Machine). As a special Lightning Chain, it establishes direct connections with all regular Lightning Chains in the network, forming an efficient star topology structure. This design makes the System Chain the central hub of Super Bitcoin.
The System Chain is primarily responsible for incentivizing Lightning Network nodes and coordinating cross-chain interoperability, effectively managing the entire network to ensure its efficient operation. In terms of node incentives, the System Chain implements a complex and sophisticated mechanism. It uses a dynamic reward algorithm that adjusts reward distribution based on the activity level, liquidity provided, and overall contribution to the network. During this process, the System Chain considers multi-dimensional evaluation metrics, such as the node’s uptime, transaction throughput, and routing efficiency.
In terms of cross-chain interoperability, the System Chain plays a key coordination role, facilitating seamless interactions between different Lightning Chains. It implements a secure cross-chain communication protocol based on Hashed Time Lock Contract (HTLC), ensuring the security and reliability of message transmission. Additionally, the System Chain introduces an atomic swap mechanism, which effectively prevents potential loss of funds during cross-chain asset transfers. Furthermore, by defining a unified cross-chain asset standard, the System Chain simplifies the asset mapping process between different Lightning Chains, further improving the efficiency and convenience of cross-chain operations.
6. Economic Model
The economic model of BEVM (Bitcoin-Enhanced Virtual Machine) combines Bitcoin’s issuance mechanism with the functional characteristics of the Lightning Network. It aims to address the sustainable competitiveness of Super Bitcoin and provide a long-term incentive system for the Lightning Network.
At the core of this model is the combination of Lightning Network node incentives and a staking-mining mechanism. Lightning Network nodes that establish state channels with the BEVM network can participate in staking mining. Staking mining uses a Verifiable Random Function (VRF) to determine mining probabilities, rather than distributing rewards proportionally based on the staked amount.
During the staking mining process, participants stake BTC in state channels, and the system calculates the mining probability based on the VRF. For example, if three nodes stake 100 BTC, 10 BTC, and 1 BTC, their respective mining probabilities would be 90.09%, 9.01%, and 0.90%. This mechanism ensures that smaller stakers also have a substantial opportunity to earn rewards. A dedicated whitepaper on the economic model will be released for this section, so this document will not go into further details.
7. Future Development
7.1 Short-Term Goals
The short-term goals of Super Bitcoin focus on implementing core functionalities and building the necessary infrastructure. By realizing the proposed five-layer protocol, we will introduce smart contract functionality based on the Lightning Network while sharing BTC consensus security. For users, participating in Super Bitcoin ensures that the BTC they hold remains fully under their control. At the same time, they will be able to use BTC, Taproot Assets, and other native assets within smart contracts.
7.2 Long-Term Vision
The long-term vision of Super Bitcoin is to build a global Value Internet that shares BTC consensus security. We aim to design an incentive mechanism through an innovative economic model, promoting widespread use of Lightning Network nodes. Furthermore, we are committed to deeply integrating existing blockchain ecosystems with Super Bitcoin, enabling the free flow and interaction of BTC assets. By doing so, we aim to create a secure, efficient, and interoperable blockchain ecosystem where BTC becomes the core, and all blockchain consensus models share the security of the Bitcoin network. Ultimately, our goal is to enable the Bitcoin network to scale infinitely while maintaining decentralization.
7.3 Potential Challenges and Solutions
Super Bitcoin faces several potential challenges in achieving its goals. Transforming Lightning Network nodes into a full-fledged network involves complex technical challenges that require extensive testing. Another challenge is designing a better economic incentive model to attract enough Lightning Network node operators to adopt Super Bitcoin. Ensuring seamless communication and atomic swaps between different node networks is also crucial, and the team will focus on developing standardized protocols and interfaces to enhance network interoperability. As the system’s complexity increases, maintaining network security will become more challenging. Super Bitcoin will adopt rigorous security audit processes and consider introducing advanced cryptographic technologies to strengthen system security. As the number of lightning chains grows, managing the state and interaction between networks may pose scalability challenges. By actively addressing these challenges, Super Bitcoin aims to bring revolutionary changes to the Bitcoin and Lightning Network ecosystems, creating a more flexible, efficient, and scalable infrastructure.
8. Conclusion
The five-layer architecture introduced by Super Bitcoin not only solves the problem of existing BTC Layer 2 solutions not being able to share Bitcoin's consensus security but also addresses the limitation of the Lightning Network being restricted to payment scenarios. It perfectly combines the shared BTC consensus security with smart contract functionality. Our protocol uses the Bitcoin network as the core, ensuring the highest level of security. It leverages the Lightning Network to construct an efficient communication layer, significantly improving scalability and flexibility while preserving the security of the native BTC consensus. By introducing Taproot Consensus as the extension layer, it abstracts Bitcoin and Lightning Network data to provide actionable data for the upper layers. Through the multi-chain fusion layer formed by lightning chains, we achieve a "multi-chain interconnection" supporting the free flow of cross-chain assets. The application layer offers developers a rich set of tools, fostering the development of a diverse DApp ecosystem. Combined with the innovative VRF-based staking mining mechanism, Super Bitcoin adds an incentive layer to the Lightning Network and allows the decentralized Bitcoin network to have unlimited flexibility and scalability.
9. References
[1] Nakamoto, S. (2008). "Bitcoin: A Peer-to-Peer Electronic Cash System." https://bitcoin.org/bitcoin.pdf
[2] Poon, J., & Dryja, T. (2016). "The Bitcoin Lightning Network: Scalable Off-Chain Instant Payments." https://lightning.network/lightning-network-paper.pdf
[3]Habermeier, S., et al. (2020). "Substrate: A modular framework for building blockchains." https://www.parity.io/substrate/
[4]Wuille, P., Nick, J., & Towns, A. (2019). "Taproot: SegWit version 1 spending rules." https://github.com/bitcoin/bips/blob/master/bip-0341.mediawiki
[5] Nick, J., Seurin, Y., & Wuille, P. (2020). "Schnorr Signatures for secp256k1." https://github.com/bitcoin/bips/blob/master/bip-0340.mediawiki
[6]Wood, G. (2016). "Polkadot: Vision for a heterogeneous multi-chain framework." https://polkadot.network/PolkaDotPaper.pdf
-
-
 @ 09fbf8f3:fa3d60f0
2024-09-08 13:17:43
@ 09fbf8f3:fa3d60f0
2024-09-08 13:17:43由于telegram的政策调整,不允许滥用telegraph匿名上传图片了。 导致之前通过telegraph搭建的图床无法上传(已上传的能正常查看)。
有人通过原项目的基础上分支另外项目,可以通过频道上传图片。
项目是通过cloudflare pages搭建的。 - 项目地址:https://github.com/MarSeventh/CloudFlare-ImgBed
项目的教程很详细,具体去看项目教程。
telegram设置:
- 需要有telegram账号
- 通过@BotFather创建一个telegram机器人,并获取api key。
- 创建一个频道,获取频道id,通过转发一条消息到 @VersaToolsBot机器人可以查看频道id。
- 一定要添加创建的机器人到频道作为管理员才能使用。
cloudflare的设置
- 通过git项目部署,设置变量:TG_BOT_TOKEN和TG_CHAT_ID就基本可以使用了。
- 如果需要后台,需要添加kv空间,并在设置里面的函数,选择对应的kv空间,如图:

- BASIC_USER 后台登陆名
- BASIC_PASS 后台密码
- AUTH_CODE 鉴权,防止别人使用,设置后,别人使用必须输入这个。
其他
- 成人内容屏蔽
- pico 使用api接口 去项目地址看
最后
我搭建的地址: https://imgbed.lepidus.me
-
 @ 1bda7e1f:bb97c4d9
2024-10-24 04:48:52
@ 1bda7e1f:bb97c4d9
2024-10-24 04:48:52Tldr
- Nostr relays help users post and read notes on the network
- Relay operators have launched a variety of relays for you to use
- You too can launch your own relay for any reason you like
- Launching your own relay gives you a lot of power in how you use Nostr
- Many relay softwares exist for you to use
- I launched a personal relay using HAVEN relay software on my VPS
- I am now more in control of saving notes, cutting spam, and protecting my privacy
- My personal relay is now hosted at relay.rodbishop.nz
What are Nostr Relays Anyway?
When you're a user of a social network, you post and read notes from other users on the network. In a centralised network like Twitter or Instagram the company's servers receive all user's notes and relay them to other users. On Nostr, there is no single company's servers to relay messages, so instead the task is taken up by relay operators.
Anyone can be a relay operator and they can run a relay for any purpose. When you start using Nostr you will usually be connected to any one of a number of "public" relays, and be able to post and receive notes from users on the network via these.
Configuring these relays can tailor your experience somewhat–for example the client Nostrudel allows you to select from Western or Japanese relay set.
It is also possible to set up your own relay to use for your own purposes. All kinds of people have launched relays for all kinds of purposes. For example, to:
- Power your own client
- Support your community
- Run a for-profit relay business
- Relay a certain a type of content you need
- Back up your own notes, decrease spam, or increase privacy
- Curate your own social feed with your own algorithm
Relay instances available to connect with
Today is an interesting time in relay-ops. The evolution of the technology has inspired users to experiment with diverse types of relays tailored to various needs. As a result there are very many relay instances in operation and available to connect with.
A few sites try to collate which relays are in operation, like nostr.info and xport.top and sesseor's relay list . These lists are long (Sessor's list counted 2,500+ relays) and it's not clear to me whether it's even possible to be comprehensive as relays may join or leave the network all the time.
Broadly speaking, relays might be available for different users to use in different ways:
- A relay where anyone can post, like relay.damus.io
- A paid relay where anyone can post after payment, to cut spam, like nostr.wine
- A "web of trust" relay where anyone can post if they are related to the owner's social graph, to cut spam, like nostrelites.org
- A speciality relay where a particular community can post, like nostr.com.au for #austriches (Australians)
- A relay where anyone can post just specific content, like purplepag.es for user profiles only
- A team relay for your company or organisation only
- A personal relay for your own personal use
Nostr.Band shows which of these available relays are most popular, such as relay.damus.io and nos.lol and eden.nostr.land
Relay softwares for you to launch your own
You may decide to launch you own relays, and if you do there are many different relay softwares to choose from:
- Simple, like Bucket (<100 lines of code)
- Widely used, like Nostream (top ranked on Github)
- Customisable, like Khatru (a framework for customised relays)
- Specialised, like HAVEN or Team Relay (for personal or teams relays, based on Khartu)
You can run these on your own server, or local machine, or phone or with a third-party host.
Aljaz provides a great resource with 45+ relay softwares to choose from.
In summary, at a high level,
- Anyone can connect to any of the relay instances that are available for them to use
- Anyone who wants to launch their own can select the relay software that best suit their needs, launch an instance, and have it used by whichever users they like
Reasons to Run Your Own Relay
As a normal user of a Nostr client there's no obligation to run a relay. But having your own relay does give you more power.
For my own journey down the #nostr rabbit hole, I was looking for a relay to:
- back up my notes
- decrease spam
- increase my privacy
- learn skills I could later use for running a community or team or paid relay
Backing up notes – When you post notes to a public relay there's no guarantee that the relay is going to keep them long-term. It's job is relaying your notes to other clients, not storing them. Running your own relay allows you to keep your notes online.
Decrease spam – To first spam we can use a "Web of Trust" model–in which users endorse other users as trustworthy. A "Web of Trust" relay will reject notes from parties too far removed from your network. Running your own relay makes you more difficult to spam.
Increasing privacy – When you connect to a public relay, they can determine personal information about you, such as your IP address. Running your own relay keeps things more private.
For communities and teams and paid relays – Many opportunities exist to tailor relays to certain users needs, be they businesses or communities or as a for-profit business. For me, I am hoping that running my own relay helps me learn skills I can use in these kinds of further ventures.
To start I decided to focus on a personal relay. However, when I really got under the hood, it turned out I would need multiple relays not just one.
The outbox model
Mike Dilger proposed the outbox model (originally called the gossip model) as a way for users to engage with the wider Nostr network. It's a great model that is helpful to understand, as it suggests to establish different relays for different purposes.
Many clients and relay softwares have now adopted and continued to elaborate on this model. An example is to run specialised relays for Outbox, Inbox, Chat and Private needs.
Outbox Relay (also called Home Relay)
- This relay is for notes you have written, so that everyone knows where to find your notes
- In a set up where you are running your own, this relay is restricted so that only you can post to it, and you should set up your clients to post your notes to it
- An advanced version may take any notes received to this relay and "blast" them to other public relays so that your notes get wider reach
Inbox Relay (also called Public Relay)
- This relay is for public notes that other users want you to see, so that you always find notes that are relevant to you, including all replies, comments, likes, and zap payments
- In a set up where you are running your own, this relay is where you should look for notes relevant to you, and you should set up your clients to read from it
- An advanced version may search other public relays for notes that tag you, and import them into this relay so that you never miss a relevant note
Chat Relay (also called Direct Message Relay)
- This relay is for private direct message notes from other users, so that you always find your direct messages and so that they stay private
- In a set up where you are running your own, this relay is restricted so that only you can read from it, and you should set up your clients to read from it
- An advanced version may cut spam by only accepting direct messages from other users within your Web of Trust
Private Relay
- This relay is for your private use only, so that you can store private drafts or thoughts
- Only you can write to it and only you can read from it (and so, it is a bit mis-named as it does not actually relay anything to anywhere at all)
- In a set up where you are running your own, it gives you true privacy for these notes
In summary as a user
- I post my notes to my outbox relay. Network users can read them there, and if the relay is advanced it will also blast the notes out to other relays on the network
- I read from my inbox relay. Network users know to reach me there, and if the relay is advanced it will also bring me notes from the wider network
- I can have private direct message conversations with others in my chat relay.
- I can save private notes in my private relay
For me, this model has a lot of appeal and I went looking for a personal relay which adopted this model and contained all of these features.
HAVEN as a personal relay
I decided to go with HAVEN relay software.
HAVEN is all four of the above relays in one–outbox, inbox, chat and private. It contains advanced features like blasting your notes from outbox to other relays, importing notes from other relays to your inbox, and preventing spam with Web of Trust.
HAVEN is written by Utxo the Webmaster . It is based upon the Khatru relay framework by Fiatjaf
Setting up HAVEN as a Personal Relay
I am mostly non-technical, but on my #Nostr journey I have been having success with technology set ups that use Docker.
- I have a cheap VPS which currently runs Albyhub and Phoneixd with Docker,
- My objective was to set up HAVEN to run alongside it, in a separate Docker on the same server. HAVEN does not include Docker by default, but Sebastix published a fork with Docker support.
To get HAVEN up and running in Docker on your VPS:
- Clone and configure HAVEN with the right variables
- Launch it in Docker on your VPS
- Check the URLs and logs to see your HAVEN running
- Configure a subdomain to point to the VPS
- Configure the VPS to reverse proxy to the Docker port
- Configure the relays in your favourite Nostr client
- Post a note to your outbox and see if it blasts!
Running HAVEN
I cloned Sebastix fork to start.
git clone -b docker_compose_support https://github.com/nostrver-se/haven.git cd havenThe software sets up all environment variables in the
.envfile, and comes with an.env.examplefile. Duplicate and rename the file to.env. Within the.envfile you need to set up the environment variables. The file is long but it contains lots of repetition and for the most part defaults can be retained–only a few changes are required:- Replace all instances of the default user npub with your own (for me,
npub1r0d8...) - Change the default relay URL to your own (for me,
relay.rodbishop.nz) - Replace all instances of the default name in the relay names (for me, "Rod's ...")
- Replace all instances of the default profile image with your own
To enable automatic blasting from your outbox, and importing to your inbox, the software comes with an example list of relays to blast and import from. See
relays_blastr.example.jsonandrelays_import.example.json. To use these features simply duplicate and rename these files torelays_blastr.jsonandrelays_import.jsonrespectively. Within these files you can specify the public relays of your choice. I simply used the default list.There are other features available, such as backups and initial imports, but I decided to handle these later. To start with I wanted to launch the relay and test it.
To launch the relay run Docker Compose.
docker-compose up -d docker logs haven-relayThen you should explore the logs in the command line and the ports in your browser to see if it launched successfully. The logs should show your web of trust has been built successfully and the browser should show simple landing pages.
The logs should show that the relay has queried the network and built a web of trust from your followers. Mine looked as follows.
2024/10/14 12:02:08 🌐 building web of trust graph 2024/10/14 12:02:16 🫂 total network size: 13296 2024/10/14 12:02:16 🔗 relays discovered: 335 2024/10/14 12:02:17 🌐 pubkeys with minimum followers: 9394 keysYour browser should show you have four relays in operation, for example as follows.
your_IP_address:3355(your outbox or home relay)your_IP_address:3355/private(your private relay)your_IP_address:3355/chat(your direct message relay)your_IP_address:3355/inbox(your inbox relay)
That's it. Your relay is online.
Connecting HAVEN
Now all that remains is the plumbing to connect your domain, relay, and Nostr clients together.
Configure DNS
First, configure your domain. At a high level –
- Get your domain (buy one if you need to)
- Get the IP address of your VPS
- In your domain's DNS settings add those records as an A record to the subdomain of your choice, e.g.
relayas inrelay.your_domain_name.com, or in my caserelay.rodbishop.nz
Your subdomain now points to your server.
Configure reverse proxy
Next, you need to redirect traffic from your subdomain to your relay at port
3355.On my VPS I use Caddy as a reverse proxy for a few projects, I have it sitting in a separate Docker network. To use it for my HAVEN Relay required two steps. I am sure that the way I do this is not very elegant, but it worked. If you prefer a different method, the HAVEN readme also comes with instructions on how to perform a similar setup using nginx.
For my method, my steps were as follows:
- Add configuration to Caddy's
Caddyfileto tell it what to do with requests for therelay.rodbishop.nzsubdomain - Add the Caddy Docker network to the HAVEN
docker-compose.ymlto make it be part of the Caddy network
For the addition to the
Caddyfile, I used as follows:relay.rodbishop.nz { reverse_proxy haven-relay:3355 { header_up X-Forwarded-For {remote} header_up X-Forwarded-Proto {scheme} header_up X-Forwarded-Port {server_port} } }For the addition to the
docker-compose.yml, I used as follows:``` networks: - caddy # Added this line to services to connect to the Caddy network
networks: caddy: external: true # Added this to section specify the Caddy network ```
Once your DNS configuration and reverse proxy setup are completed, you should now be able to access your Nostr client at
relay.your_domain_name.com. For my set up, this wasrelay.rodbishop.nz.Connecting your Nostr client
Most Nostr clients allow you to specify any relay you choose. My go-to client at the moment is Amethyst on Android. Amethyst allows you to specify discrete relays for each role in the outbox model which ties up very neatly with HAVEN.
- In the sidebar, select Relays
- For "Public Outbox/Home Relays" enter
relay.your_domain_name.com - For "Public Inbox Relays" enter
relay.your_domain_name.com/inbox - For "DM Inbox Relays" enter
relay.your_domain_name.com/chat - For "Private Home Relays" enter
relay.your_domain_name.com/private - Click Save to broadcast your new relays to the Nostr network.
Your new relay configuration is now live.
Testing your relay
Lastly, it's time to test. Amethyst provides a simple method to test this as it allows you to configure the relays used on each post.
- Create a test note, and then before you post it, edit your relays using the icon at the top
- Turn off all relays except your own outbox relay, and post the note
- Access your HAVEN docker logs with
docker logs haven-relayand see if there is a log to indicate if the note was received and blasted to other public relays - Copy the
neventof the note, and attempt to find it in another client
If you're in luck, you may see something like this (the blasted note, and then users on the network responding to the note in turn).
2024/10/22 00:12:23 🔫 blasted 95c477af7e6b612bf5d1d94309d2d57377a0a67d2181cfbb42a2e3fbc0feeaaf to 26 relays 2024/10/22 00:13:50 🤙 new reaction in your inbox 2024/10/22 00:14:42 🫂 new reaction in your inbox 2024/10/22 00:14:45 ✅ new reaction in your inbox 2024/10/22 00:15:12 💜 new reaction in your inbox 2024/10/22 00:17:03 ✅ new reaction in your inbox 2024/10/22 00:17:03 🫂 new reaction in your inbox 2024/10/22 00:17:55 🫂 new reaction in your inbox 2024/10/22 00:19:02 📰 new note in your inboxThat's it. If you followed this successfully your personal relay is up and running.
What I did wrong so you don't have to
My first relay was too public
This blog comes after much trial and error. The first error I made was I set up a relay to use as a personal relay, but without any restrictions on use. I very quickly found other people discovered and started using my relay to save their own notes! This was unintended and I had to take it down.
Unfamiliar with Go language
I am mostly non-technical, and completely unfamiliar with Go. I got the project up and running with Go on my localhost–with a lot of help from my AI–but I then completely failed in migrating this to my VPS. Moving to Docker made the difference for me here.
I failed a few times due to a messy folder
After messing with Go, I moved to the Docker setup, but I started my work from a messy folder which contained remnants of the Go build, which caused various failures. Deleting the folder and cloning again from scratch solved the issue.
Trouble with Nostr.wine
I subscribe to the Nostr.wine paid relay, and I initially added it to the list of relays in my blaster. However, it didn't work, and the logs showed an error as follows
CLOSED from wss://nostr.wine: 'auth-required: this relay only serves private notes to authenticated users'It seems my npub's subscription to Nostr.wine is not enough for it to permit my relay to blast notes to it. In the end, I removed Nostr.wine from my relay config, and kept Nostr.wine as a separate entry in my Client's outbox settings.
Failed to create web of trust graph
When I first launched the relay on my VPS, HAVEN failed to complete the Web of Trust graph, with a log that looked as follows (note the zeroes). As a result, no one would have been able to send me DM's to my Chat relay (it would flag every message as spam).
2024/10/14 12:02:08 🌐 building web of trust graph 2024/10/14 12:02:16 🫂 total network size: 0 2024/10/14 12:02:16 🔗 relays discovered: 0 2024/10/14 12:02:17 🌐 pubkeys with minimum followers: 0 keysI never got to the bottom of why this was. In the process of trying to fix it I rebuild the container, and on the rebuild it spontaneously worked. Accordingly my lesson learned is "if in doubt, turn if off and on again".
Failed to run --import function
HAVEN comes with a function to import all your old notes from other public relays to your own outbox relay. When I run it I get an error as follows:
panic: Cannot acquire directory lock on "db/private". Another process is using this Badger database. error: resource temporarily unavailableI have yet to work out the solution for this, and will update this note when I do so!
What's Next?
Over the past four blogs I have
- Mined a Nostr pubkey and backed up the mnemonic
- Set up Nostr payments with a Lightning wallet plus all the bells and whistles
- Set up NIP-05 and Lighting Address at my own domain
- Set up a Personal Relay at my own domain
This feels like a very comprehensive personal set up now. Also, I have uncovered some new rabbit holes and feel like I have some projects to tackle. Perhaps one of these?
- Set up a personal homepage with my Nostr feed to round-out my rodbishop.nz domain
- Experiment with different signers like Amber and Nsec.app and NFC cards
- Set up a paid relay for #austriches (Australians and Kiwis on Nostr)
- Set up a team relay to experiment with Nostr for business or community projects
- Or something else ... ?
Please be sure to let me know if you think there's another Nostr topic you'd like to see me tackle.
Pura vida Nostr.
-
 @ c11cf5f8:4928464d
2024-09-08 09:08:04
@ c11cf5f8:4928464d
2024-09-08 09:08:04
Here we are again with our The Magnificent Seven, trying to give you a hit of what you missed this past month in the ~AGORA territory.
Top-Performing Ads
Drumroll please 🥁 ... for the most engaging ones:
01[SELL] 1 Million Products, Travel Agency, Concierge and Cars - ShopinBit.com by @shopinbit02[SELL] Satoffee⚡️☕️ Cafeteras automáticas que aceptan Bitcoin Lightning 🇪🇸 🌐 by @VEINTIUNO03[⚖️SELL] Hand-Made Flecktarn Pouch(es) by Fabs04[OFFER] Proton Wallet - 3 invites left by @npub1q67p49masrcjf__d7qaq6mwh0q05[SELL] Bitcoin Accepted Here – Unisex organic cotton Black T-shirt by @VEINTIUNO06[FOR SALE] Playstation 2 (PS2) Games - Excellent Condition - Pay In SATS!!! by @watchmancbiz07[OFFER] Happy Bitcoin Infinity Day by @thebullishbitcoiner
In case you missed
Here some interesting post opening conversation and free speech:
This edition winner look's @proofoftaste, with his request for help finding a way to get a local product delivered to his country. The challenge was that the producer, required an ID number on checkout! Pretty unusual... or it will be soon the norm?
Thanks a lot for @supratic for being so active in the territory and sharing so many topics and articles about commerce and law, basically giving us a hit on how the world is currently ruled, pretty fascinating!
01Can someone in Italy help me get my favourite sauce to Germany? by @proofoftaste02The History of Banking – Ernest Rauthschild by @supratic0310 Hidden Rules of Commerce by @supratic04How to Start Your Own Micronation by @supratic05[Understanding the One People's Public Trust: A Beginner's Guide to the OPPT(https://stacker.news/items/641554/r/AG) by @supratic06A Bank Whistleblower called me... by @supratic07One Stupid Fu*K 🥒 Contract Killer Course 2.0 - Brandon Joe Williams by @02a0eb55b5
🏷️ Spending Sunday is back! https://stacker.news/items/653241/r/AG
Share your most recent Bitcoin purchases of just check what other stackers are buying with their sats!
Just a reminder for you all
To incentivize more conversation and a more libre mindset, we decided to adopt the zapshare approach, so we'll split the rewards of this TM7 to the best contributors plus zaps to the posts that offer much PoW when posting.
Create your Ads now!
This territory aims to connect stackers and curious buyers online and IRL for exclusive P2P Bitcoin deals. Have fun checking what else stackers are shilling globally in the ~AGORA. This is a great time for you to make some space un-dusting some stuff that has been sitting there for too long and get some sats for it!
Let's start something new? Hit one of the links below to free your mind:
- 💬 TOPIC for conversation,
- [⚖️ SELL] anything! or,
- if you're looking for something, hit the [🛒 BUY]!
- [🧑💻 HIRE] any bitcoiner skill or stuff from bitcoiners
- [🖇 OFFER] any product or service and stack more sats
- [🧑⚖️ AUCTION] to let stackers decide a fair price for your item
- [🤝 SWAP] if you're looking to exchange anything with anything else
- [🆓 FREE] your space, make a gift!
- [⭐ REVIEW] any bitcoin product or LN service you recently bought or subscribed to
Or contact @AGORA team on nostr DM and we'll help you publish a personalized post.
originally posted at https://stacker.news/items/676777
-
 @ c11cf5f8:4928464d
2024-09-08 08:35:16
@ c11cf5f8:4928464d
2024-09-08 08:35:16Let's hear some of your latest Bitcoin purchases, feel free to include links to the shops or merchants you bought from too.
If you missed our last thread, here are some of the items stackers recently spent their sats on.
originally posted at https://stacker.news/items/676757
-
 @ a012dc82:6458a70d
2024-10-24 02:48:43
@ a012dc82:6458a70d
2024-10-24 02:48:43Table Of Content
-
Project A: Solar-Powered Mining Farms
-
Project B: Hydroelectricity-Powered Mining
-
Project C: Waste Heat Recovery
-
Project D: Energy-Efficient Mining Hardware
-
Project E: Proof of Stake (PoS) Consensus
-
Project F: Carbon Offset Initiatives
-
Conclusion
-
FAQ
The rising popularity of Bitcoin has raised concerns about its environmental impact. Traditional Bitcoin mining processes consume vast amounts of energy, contributing to carbon emissions and environmental degradation. However, there is a growing movement towards sustainable mining practices that aim to minimize the ecological footprint of cryptocurrency production. In this article, we will delve into the world of green Bitcoin mining and highlight six exciting projects that are leading the charge towards sustainable practices.
1. Project A: Solar-Powered Mining Farms
With solar energy being one of the cleanest and renewable sources available, Project A aims to harness its power for Bitcoin mining. By setting up solar-powered mining farms, this project significantly reduces reliance on fossil fuels and minimizes carbon emissions. Additionally, excess solar energy can be stored for later use, making mining operations more resilient and sustainable.
2. Project B: Hydroelectricity-Powered Mining
Project B taps into the potential of hydroelectricity, utilizing the power of flowing water to generate electricity for Bitcoin mining. Hydroelectric power is not only renewable but also provides a consistent and reliable energy source. By harnessing this form of energy, Project B aims to achieve sustainable mining operations while reducing the carbon footprint associated with traditional mining methods.
3. Project C: Waste Heat Recovery
Project C focuses on utilizing waste heat generated from industrial processes for Bitcoin mining. By capturing and repurposing this excess heat, mining operations become more energy-efficient and environmentally friendly. This approach not only reduces carbon emissions but also maximizes the use of resources that would otherwise go to waste, promoting a circular economy.
4. Project D: Energy-Efficient Mining Hardware
Project D tackles the sustainability challenge by developing energy-efficient mining hardware. By optimizing the design and performance of mining equipment, this project aims to reduce energy consumption without compromising mining capabilities. The use of advanced technologies and materials enables miners to achieve higher processing power with lower energy requirements, leading to more sustainable mining operations.
5. Project E: Proof of Stake (PoS) Consensus
Project E explores an alternative consensus mechanism called Proof of Stake (PoS), which requires significantly less energy compared to the traditional Proof of Work (PoW) algorithm. Instead of relying on computational power, PoS validates transactions based on the amount of cryptocurrency held by a participant. This shift in consensus mechanism can drastically reduce energy consumption and make Bitcoin mining more environmentally friendly.
6. Project F: Carbon Offset Initiatives
Project F recognizes that some carbon emissions may still be unavoidable in the mining process. To mitigate this impact, they focus on supporting carbon offset initiatives. By investing in projects that reduce or remove carbon dioxide from the atmosphere, such as reforestation or renewable energy projects, Project F aims to offset the environmental impact of Bitcoin mining, making it more sustainable in the long run.
Conclusion
As the demand for Bitcoin continues to rise, so does the need for sustainable mining practices. The projects mentioned above represent just a glimpse of the innovative solutions being developed to make crypto mining more environmentally friendly. By harnessing renewable energy sources, optimizing mining equipment, and exploring alternative consensus mechanisms, these projects are leading the race for sustainable mining. Through their efforts, they are shaping a future where Bitcoin and other cryptocurrencies can coexist harmoniously with a greener planet.
FAQ
What is sustainable mining? Sustainable mining refers to the practice of conducting mining operations while minimizing the negative environmental impact. It involves adopting strategies and technologies that reduce energy consumption, carbon emissions, and other ecological footprints associated with mining activities.
How does solar-powered mining work? Solar-powered mining harnesses the energy from the sun using solar panels to generate electricity. This clean and renewable energy source powers the mining equipment, reducing reliance on fossil fuels and minimizing carbon emissions.
What is the difference between Proof of Stake (PoS) and Proof of Work (PoW)? Proof of Stake (PoS) and Proof of Work (PoW) are two different consensus mechanisms used in blockchain networks. PoW relies on computational power to validate transactions, while PoS validates transactions based on the amount of cryptocurrency held by participants. PoS requires significantly less energy compared to PoW, making it more environmentally friendly.
How can waste heat recovery be used for mining? Waste heat recovery involves capturing and repurposing excess heat generated from industrial processes. This heat is used to power mining equipment, making the mining operations more energy-efficient and sustainable. It reduces the need for additional energy sources and minimizes waste.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com ** X: @croxroadnews**
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 6bae33c8:607272e8
2024-09-07 22:09:27
@ 6bae33c8:607272e8
2024-09-07 22:09:27With all five of my football drafts/auctions in the books, here's the portfolio I've amassed for 2024, not including the RotoWire Dynasty League:
Links: BCL1, BCL2, BCL3, Steak League, Primetime
Players in whom I have the most shares:
QB: Justin Fields (4), CJ Stroud (2), Anthony Richardson (2), Tua Tagovailoa (2)
RB: Jonathan Brooks (2), Brian Robinson (2), Jerome Ford (2), Jordan Mason (2), JK Dobbins (2), Khalil Herbert (2), Dalvin Cook (2)
WR: Stefon Diggs (5), Ja’Marr Chase (3), Rashid Shaheed (3), Ladd McConkey (2), Roman Wilson (2)
TE: Jonnu Smith (3)
K: Younghoe Koo (3), Harrison Butker (2)
D: Giants (4)
Notes:
Obviously, I thought Stefon Diggs was mispriced, though I only had to pay close to what I thought he was worth in the Primetime — in the rest of the leagues he fell to me at ADP or below. He and Ja’Marr Chase are massively important to me this year, and to a lesser extent CJ Stroud.
I also have Justin Fields and the Giants defense everywhere, but both were essentially free, and I could swap them out without issue. I also have a lot of Younghoe Koo, but he too could obviously be swapped out. I like having a couple key players to build around rather than five disparate teams. Of course if Diggs gets hurt or turns out to be washed up, it’ll be rough, but in some ways it’s like the old days where you had only one team, and you had to live and die with it.
Prominent Players I Don't Have (bold is by choice):
Bijan Robinson, Tyreek Hill, Breece Hall, Amon-Ra St. Brown, Justin Jefferson, Garrett Wilson, A.J. Brown, Jonathan Taylor, Puka Nacua, Davante Adams, Saquon Barkley, Chris Olave, Rashee Rice, Kyren Williams, Travis Etienne, Cooper Kupp, Isiah Pacheco, Michael Pittman, Nico Collins, DK Metcalf, Mike Evans, Deebo Samuel, Josh Allen, DJ Moore, Brandon Aiyuk, Derrick Henry, Zay Flowers, James Cook, Terry McLaurin, Kenneth Walker, Xavier Worthy, Amari Cooper, Josh Jacobs, Trey McBride, George Pickens, Lamar Jackson, Christian Kirk, Tee Higgins, Calvin Ridley, Rachaad White, Jayden Reed, Diontae Johnson, Travis Kelce, Joe Mixon, Alvin Kamara, Christian Watson, Jalen Hurts, Aaron Jones, Patrick Mahomes, David Montgomery, Zamir White, Keenan Allen, Kyle Pitts, D’Andre Swift, George Kittle
Past Portfolios:
-
 @ 13e63e99:25525c6a
2024-10-24 02:44:17
@ 13e63e99:25525c6a
2024-10-24 02:44:17
Bitcoin has experienced a notable 129.2% price increase this year, with a solid 8.9% gain this month alone. This rise has been driven by an improving risk-on sentiment in the market, spurred by better-than-expected earnings from major Wall Street firms. The strong earnings reports have helped bolster investor confidence, contributing to a broader appetite for riskier assets like Bitcoin, which has been increasingly seen as a hedge against traditional financial uncertainties.
Additionally, growing speculation around a potential Federal Reserve rate cut in November has further fueled Bitcoin's momentum. Investors are factoring in the possibility that the Fed may pivot from its current monetary tightening, which could lead to a more favorable macroeconomic environment for assets like Bitcoin that thrive in low-interest-rate scenarios.

Moreover, the political landscape is playing a significant role in driving Bitcoin's price action. The increasing odds of pro-Bitcoin candidate Donald Trump winning the 2024 presidential election are adding to market optimism. Trump's favorable stance on cryptocurrency and his potential return to office are viewed by many investors as a catalyst for more crypto-friendly regulations and policies, further boosting Bitcoin's appeal.
In combination, these factors—improving market sentiment, potential Fed rate cuts, and political developments—are creating a bullish outlook for Bitcoin as we move toward the end of 2024. Investors are increasingly viewing Bitcoin as both a hedge and a speculative asset, positioning it well in the current economic and political climate.
Reference: Yahoo Finance

Tesla transfers $765 million to self-custody wallets, highlighting the importance of Bitcoin self-custody. Bitcoin self-custody refers to the practice of directly controlling and managing your own Bitcoin holdings, rather than relying on a third-party custodian such as a cryptocurrency exchange or wallet service. When you hold Bitcoin in self-custody, you are responsible for securely storing your private keys—unique cryptographic codes that grant access to your Bitcoin and allow you to send or spend it. This approach gives individuals full control over their assets and eliminates the need to trust a centralized institution with their funds.
Self-custody is a critical component of Bitcoin’s ethos, which emphasizes decentralization, financial sovereignty, and the ability to own and transfer wealth without reliance on intermediaries. By opting for self-custody, individuals are empowered to truly "own" their Bitcoin, free from the risks associated with third-party custodians, such as hacks, mismanagement, or insolvency. The mantra "Not your keys, not your coins" reflects the idea that if someone else holds your private keys, they effectively control your Bitcoin, and you are at risk of losing access.
The Importance of Multisignature in Bitcoin Self-Custody
While self-custody offers enhanced control and security, it also comes with the responsibility of safeguarding your private keys. Losing access to these keys means losing access to your Bitcoin permanently, which can be a daunting prospect. This is where multisignature (multisig) technology plays a crucial role in bolstering the security of Bitcoin self-custody.
Multisignature refers to a security feature that requires multiple private keys to authorize a Bitcoin transaction, rather than relying on a single key. For example, a 2-of-3 multisig setup might require two out of three designated keys to approve any movement of funds. This adds an extra layer of protection in several ways:

-
Enhanced Security: Multisig helps mitigate the risk of a single point of failure. If one key is lost, stolen, or compromised, the funds are still safe because the attacker would need access to multiple keys. This protects against theft, hacking, and loss of keys.
-
Redundancy and Backup: With a multisig setup, you can distribute your keys across different locations or devices, ensuring that even if one key is lost or damaged, you can still recover your funds using the remaining keys. For example, you might store one key on a hardware wallet, another in a safe, and give a trusted family member or service provider control of the third.
-
Shared Control: Multisig is particularly useful in shared ownership scenarios, such as for businesses, trusts, or family members who want joint control over Bitcoin holdings. It ensures that no single individual can act alone in transferring or spending the Bitcoin, which provides a governance structure and reduces the risk of rogue actors.
-
Mitigating Human Error: Managing private keys can be intimidating, especially for individuals new to Bitcoin. Multisig setups can reduce the risk of human error by allowing for the recovery of funds even if a single key is lost or forgotten. It provides a balance between the autonomy of self-custody and the security measures of traditional custodianship.
Multisignature solutions offer a powerful tool to enhance security, reduce risks, and provide flexibility in managing Bitcoin holdings. By combining self-custody with multisig, users can significantly reduce the likelihood of loss or theft while maintaining full control over their assets.Some prominent Multisig platforms: Unchained Capital, Lumin, Casa
Reference:Multis.co, Unchained Capital, Lumin, Casa

Bitcoin Hashrate Hits All-Time High, Signaling Stronger Network Security and Potential Miner Consolidation
The Bitcoin hashrate has reached a new all-time high of 791.6 exahashes per second (EH/s) on Oct. 21, reflecting the increasing security of the network. This rise, driven by advancements in mining hardware like ASICs, has been on a steady upward trend since 2021.
While a higher hashrate boosts the security of the Bitcoin network, it also increases the cost to mine 1 BTC, potentially leading to miner consolidation, especially for smaller firms with less efficient rigs. With the 2024 Bitcoin halving reducing block rewards, energy-efficient mining equipment will be essential for profitability.
Despite the rising mining costs, Bitcoin miners have not significantly increased their selling, minimal miner transfers to centralized exchanges during this period.

Reference: Ycharts, Cointelegraph
Nearly Half of Traditional Hedge Funds Now Invest in Digital Assets Amid Regulatory Clarity and ETF Launches
Nearly half of hedge funds focused on traditional assets now have exposure to cryptocurrencies, driven by clearer regulations and the launch of ETFs in the U.S. and Asia, according to the Global Crypto Hedge Fund Report by AIMA and PwC.
The report revealed 47% of traditional hedge funds now invest in digital assets, up from 29% in 2023. Of those, 67% plan to maintain their digital assets investments, while the rest intend to increase by year-end.
Hedge funds, once focused on spot trading, are now deploying more sophisticated strategies. In 2024, 58% traded crypto derivatives, up from 38% in 2023, while spot trading dropped to 25% from 69%.

Reference: Pwc
UAE Exempts Digital Assets Transactions from VAT, Aligning with Traditional Financial Services

The United Arab Emirates (UAE) has exempted cryptocurrency transactions from value-added tax (VAT), aligning the industry with several traditional financial services. Effective Nov. 15, this change retroactively applies to transactions dating back to Jan. 1, 2018. The Arabic version of the Federal Tax Authority’s update was released on Oct. 2, 2024, with the English translation following on Oct. 4.
This exemption clarifies that digital assets are not subject to the 5% VAT. It covers the exchange and transfer of ownership of cryptocurrencies, meaning all digital assets transfers and conversions are now VAT-exempt.
"The UAE has essentially classified virtual assets in the same category as traditional financial services, many of which are already VAT-exempt. This move legitimizes virtual assets," said Ankita Dhawan, a senior associate at the Métis Institute, a dispute resolution think tank.
Reference: CoinDesk, Cryptopolitan

We are going to El Salvador!
Our managing partner will be speaking at Adopting Bitcoin 2024! If you're a founder, entrepreneur, or Bitcoin enthusiast, feel free to reach out. We look forward to hearing from you!

Reference: X.com

LifPay NFC Card Manufacturing Program has officially launched!

Reference: X.com
-
-
 @ 6bae33c8:607272e8
2024-09-07 22:07:54
@ 6bae33c8:607272e8
2024-09-07 22:07:54I submitted my five picks for the Circa Millions contest today. I think it’s $6M in total prizes. I want to put a disclaimer here: I’m putting these behind a paywall not because you should pay for these picks — never pay for anyone’s picks.
If the picks were that good, whoever was making them could just print money and wouldn’t need yours. If you want to subscribe in earnest, do so because you’re interested to see who I chose and read the reasoning, not because you (erroneously) think it’s the way to get some easy winners. Or if you want to support my substack generally because you think it adds value to you. Those are fine reasons to subscribe, but doing so because you think copying my picks will make you money is dumb.
Okay that out of the way, here are the picks:
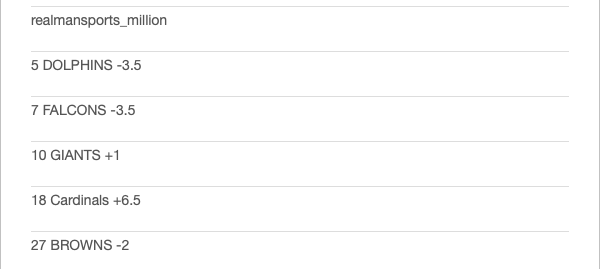
Dolphins -3.5 vs Jaguars — I like taking the Dolphins in early September, it’s hot and humid there, difficult for opposing teams to adjust to it. It’s like Lambeau Field in December, only in reverse. Moreover, the Dolphins are a veteran offense that’s played together for years, while the Jaguars are working in two new receivers.
Falcons -3.5 vs Steelers — Justin Fields is probably an upgrade over Russell Wilson at this point, but he’s haphazard and will have to learn the players and offense on the fly. The Falcons have a new QB too, but he’s an old pro, has better weapons and a better offensive line.
Giants +1 vs Vikings — The Giants have three Pro-Bowl level pass rushers, finally have a playmaking receiver and upgraded their offensive line this offseason. And yet despite facing Sam Darnold at home, they’re still getting a point.
Cardinals +6.5 at Bills — Kyler Murray is now another year removed from knee surgery, should be his usual spry self, and Marvin Harrison adds another dimension to the offense it sorely needed. The Bills will move the ball, but I think Arizona will hang with them and keep it close enough.
Browns -2 vs Cowboys — The Browns should be able to run the ball and keep the Dallas pass rush off Deshaun Watson, while Dallas’ offensive line has slipped a bit, and the Browns defense was No. 1 against the pass last year. Dak Prescott also has big home/road splits.
-
 @ 7362636d:eec5ab4c
2024-10-23 21:31:29
@ 7362636d:eec5ab4c
2024-10-23 21:31:29/start
-
 @ 6bae33c8:607272e8
2024-09-07 22:05:26
@ 6bae33c8:607272e8
2024-09-07 22:05:26This is my main event for fantasy football, the $1700 buy-in NFFC Primetime. I wound up picking 11th (I had the fourth to last choice), and while in retrospect maybe I should have opted for ninth or 10th, I wanted to get a share of Jahmyr Gibbs which is why I chose that slot. I also ran through some scenarios beforehand — what if Ja’Marr Chase (still not signed) falls — do I take him in a fourth league? But as you’ll see, the first round was complete chalk, and no windfalls whatsoever fell to me.
But I had a plan for that, and I more or less executed it.
Without further ado, here are the results:

1.11 Jahmyr Gibbs — This was the most likely scenario, and it took me about two seconds to make the pick once the top three backs and seven receivers were gone. If Gibbs (who is not on the injury report) hadn’t had a hamstring injury in camp, I’d have him close to the middle of the round rather than the end. Let’s hope he doesn’t aggravate it.
2.2 Marvin Harrison — I would have taken either Puka Nacua or Jonathan Taylor, but no breaks here either. Both went at the turn, and I knew I was taking a receiver. Starting RB-WR is the easiest build, in my opinion, but Harrison was kind of an agnostic pick. I had considered Rashee Rice, but as Alan Seslowsky pointed out, while his suspension for hit and run might not kick in until after the season (when the legal process has run its course), that could be pushed up if his lawyers negotiate a plea. Between that an the presence of so many options for the Chiefs, I went Harrison over him narrowly. But it was a close call.
3.2 Stefon Diggs — I missed Malik Nabers, Cooper Kupp, (maybe Jaylen Waddle) and De’Von Achane who went with the four consecutive picks ahead of me, so it was Diggs, Nico Collins (his teammate who has a higher ADP), DeVonta Smith or (maybe) Derrick Henry. I went Diggs who I had personally ranked the highest, wouldn’t make it back to me, who I have in every league and was part of my “unfriendly” draft plan, i.e., the Plan B I had talked about.
4.11 Tank Dell — He’s too small to hold up, but whenever he played he produced, and he gives me a bit of a Diggs hedge. I also wanted Trey McBride on this turn (as I had Marvin Harrison and could have drafted Kyler Murray — who I love this year — later), but he went on the turn. I thought about taking McBride first, but they were side by side in ADP, and my Plan B was to stack Texans, so I went Dell and took a chance.
5.2 Chris Godwin — This was the one pick I kind of regret (though it’s debatable.) I like Jayden Reed a lot, but he was half a round lower per ADP, and there was some chance I could get him on the way back. I had Godwin everywhere last year, and he was a disappointment, but apparently he’s healthier now and is going back to the slot full time where he excels.
6.11 Jaxon Smith-Njigba — The other pivot off Godwin was JSN, and sure enough he made it back all the way, though he starts off as my first bench player. That’s okay though — you need at least five viable receivers throughout the year, and I didn’t have to take C.J. Stroud because if the guy at the turn took him, I would just pivot to the Kyler Murray/Harrison stack.
7.2 C.J. Stroud — He was there, and I executed Plan B. Yes, I have a weak first three rounds by ADP, but I have Gibbs, Harrison and a big piece of the Texans passing game which I think will lead the NFL in yardage.
8.11 Jaylen Warren — I needed a second back, and Warren is one. He’s a good pass catcher and should see half the snaps in Pittsburgh.
9.2 Brian Robinson — I like Robinson as a player, he’s the undisputed early-down option on what should be a better offense. (Think Ricky Pearsall, but at RB.) Too soon? Austin Ekeler will obviously see the passing-down work unless he proves totally washed up. The Robinson pick cost me David Njoku and Brock Bowers unfortunately, which was a gamble I knew I was making.
10.11 Jordan Mason — At 29 and playing into the Super Bowl, Christian McCalfinjury was already a risk, and that he’s “expected” to play Monday night rather than 100 percent fine is worrying. Mason could be a league winner if McCaffrey goes down.
11.2 J.K. Dobbins — The Mason pick cost me Jaleel McLaughlin, so I pivoted to Dobbins who still has a high ceiling if he can ever stay healthy.
12.11 Dallas Goedert — Tight ends had flown off the board, but I was happy to get Goedert who has been valuable on a per-game basis the last couple years and is still just 29 which is late prime for the position.
13.2 Dalton Schultz — Why not stack it even harder? The Texans could throw for 5,000-plus yards, and I have three of the four top targets and the QB.
14.11 Andrei Iosivas — He’s gotten a lot of buzz in camp, seems like the No. 3 receiver right now, Tee Higgins is hurt and Ja’Marr Chase is still unsigned.
15.2 Cam Akers — The Iosivas pick cost me Jalen McMillan who would have served as Godwin insurance, but Akers could easily take an aging Joe Mixon’s job. Maybe it’s too much Houston, but if it’s a top-three offense, I’m good with it.
16.11 Justin Fields — The backup QBs had flown off the board, and Fields has too much upside to pass up. Plus he might even start Week 1 with Russell Wilson already hurt, and if he plays well, he might never look back.
17.2 Harrison Butker — It’s either the based af kicker or a Younghoe for me. Plus he locked in a decent Week 1.
18.11 Dalvin Cook — He had only 67 carries last year for a bad Jets offense. What if he isn’t as washed up as we think? He could easily win that job over Zeke Elliott and Rico Dowdle.
19.2 Jonnu Smith — TE is my weakest position, so I took another upside gamble. What if he’s the Dolphins third target?
20.11 Giants Defense — I think I took them in all four NFFC leagues. They get the Darnold Vikings at home and then Jayden Daniels in his second career start. And they have three Pro Bowl level pass rushers.
Roster By Position
QB CJ Stroud
RB Jahmyr Gibbs/Jaylen Warren
WR Marvin Harrison/Stefon Diggs/Tank Dell
TE Dallas Goedert
FLEX Chris Godwin
K Harrison Butker
D Giants
B Jaxon Smith-Njigba/Brian Robinson/Jordan Mason/JK Dobbins/Dalton Schultz/Andrei Iosivas/Cam Akers/Justin Fields/Dalvin Cook/Jonnu Smith
-
 @ c631e267:c2b78d3e
2024-10-23 20:26:10
@ c631e267:c2b78d3e
2024-10-23 20:26:10Herzlichen Glückwunsch zum dritten Geburtstag, liebe Denk Bar! Wieso zum dritten? Das war doch 2022 und jetzt sind wir im Jahr 2024, oder? Ja, das ist schon richtig, aber bei Geburtstagen erinnere ich mich immer auch an meinen Vater, und der behauptete oft, der erste sei ja schließlich der Tag der Geburt selber und den müsse man natürlich mitzählen. Wo er recht hat, hat er nunmal recht. Konsequenterweise wird also heute dieser Blog an seinem dritten Geburtstag zwei Jahre alt.
Das ist ein Grund zum Feiern, wie ich finde. Einerseits ganz einfach, weil es dafür gar nicht genug Gründe geben kann. «Das Leben sind zwei Tage», lautet ein gängiger Ausdruck hier in Andalusien. In der Tat könnte es so sein, auch wenn wir uns im Alltag oft genug von der Routine vereinnahmen lassen.
Seit dem Start der Denk Bar vor zwei Jahren ist unglaublich viel passiert. Ebenso wie die zweieinhalb Jahre davor, und all jenes war letztlich auch der Auslöser dafür, dass ich begann, öffentlich zu schreiben. Damals notierte ich:
«Seit einigen Jahren erscheint unser öffentliches Umfeld immer fragwürdiger, widersprüchlicher und manchmal schier unglaublich - jede Menge Anlass für eigene Recherchen und Gedanken, ganz einfach mit einer Portion gesundem Menschenverstand.»
Wir erleben den sogenannten «großen Umbruch», einen globalen Coup, den skrupellose Egoisten clever eingefädelt haben und seit ein paar Jahren knallhart – aber nett verpackt – durchziehen, um buchstäblich alles nach ihrem Gusto umzukrempeln. Die Gelegenheit ist ja angeblich günstig und muss genutzt werden.
Nie hätte ich mir träumen lassen, dass ich so etwas jemals miterleben müsste. Die Bosheit, mit der ganz offensichtlich gegen die eigene Bevölkerung gearbeitet wird, war früher für mich unvorstellbar. Mein (Rest-) Vertrauen in alle möglichen Bereiche wie Politik, Wissenschaft, Justiz, Medien oder Kirche ist praktisch komplett zerstört. Einen «inneren Totalschaden» hatte ich mal für unsere Gesellschaften diagnostiziert.
Was mich vielleicht am meisten erschreckt, ist zum einen das Niveau der Gleichschaltung, das weltweit erreicht werden konnte, und zum anderen die praktisch totale Spaltung der Gesellschaft. Haben wir das tatsächlich mit uns machen lassen?? Unfassbar! Aber das Werkzeug «Angst» ist sehr mächtig und funktioniert bis heute.
Zum Glück passieren auch positive Dinge und neue Perspektiven öffnen sich. Für viele Menschen waren und sind die Entwicklungen der letzten Jahre ein Augenöffner. Sie sehen «Querdenken» als das, was es ist: eine Tugend.
Auch die immer ernsteren Zensurbemühungen sind letztlich nur ein Zeichen der Schwäche, wo Argumente fehlen. Sie werden nicht verhindern, dass wir unsere Meinung äußern, unbequeme Fragen stellen und dass die Wahrheit peu à peu ans Licht kommt. Es gibt immer Mittel und Wege, auch für uns.
Danke, dass du diesen Weg mit mir weitergehst!
-
 @ 6bae33c8:607272e8
2024-09-07 22:00:17
@ 6bae33c8:607272e8
2024-09-07 22:00:17Unfortunately, I didn’t have a ton of action in this game. I had the Packers with the points and am now 0-2 to start the week in my home picking pool. I had Xavier McKinney in the Steak League which was nice as like Roquan Smith he too started the year with a pick.
But I was missing the principal scorers namely Saquon Barkley (maybe I let the nerds talk me out of him, as I had him ranked highly initially) and Jayden Reed. Barkley I’m okay with because the potential for Jalen Hurts TDs was something I hadn’t initially considered, but Reed was a major error and in fact I passed on him for freaking Chris Godwin in my Primetime last night!
I had even argued with Alan Seslowsky that Reed was the obvious choice among the Packers receivers. So seeing him go off (and he should have had a third TD, but it was called back due to something I’ve never seen before (both teams having 12 men on the field) was painful. Godwin is almost sure to have a terrible season now just to hammer home the lesson for me: Don’t worry about 10 spots of ADP, take the fucking guy you like. Stop listening to the consensus when you have a real lean.
I don’t know how many times I need to learn this lesson, but apparently at least one more!
-
Reed looked like the most electrifying receiver on the field for the Packers. He had only six targets, not including the TD called back due to the penalties, but it’s obvious he’ll get more, and the handoff he took 33-yards to the house will incentivize them to do that again too. Year 2 after the surprisingly strong Year 1. He belongs in the second round now, along with Rashee Rice.
-
Christian Watson caught a TD and will be involved, but as great an athlete as he is he doesn’t have Reed’s football skills. Romeo Doubs is just a guy, but he’s reliable, and Dontayvion Wicks had a rough game — he’s an easy cut for me.
-
Jordan Love didn’t scramble much, and the Packers settled for a ton of field goals, but he looked okay. I think once they give Reed his 10 targets, Love will have his expected numbers. (Just read on RotoWire that Love left the game for the last two plays with an unspecified leg injury, something not apparent on the 40-minute edited version. I thought they brought Malik Willis to throw a Hail Mary! Obviously, if he’s out for any length of time, all bets are off for the Packers receivers.)
-
Josh Jacobs got stuffed in short yardage early, fumbled (though the Packers recovered), but ran well and hard late and even caught two passes. I have zero shares, but he looks like a fine pick for the late-third/early fourth. His backup Emanuel Wilson looked pretty spry too. Marshawn Lloyd is a cut now too in most formats.
-
Brayden Narveson missed a key kick off the post, but got a lot of attempts. He seems to have landed in the right place for a big season.
-
Jalen Hurts was a bit sloppy with two picks and a lost fumble, never got going on the ground (seemed like the Packers were really dedicated to taking that away), and the ass-smash didn’t work as well without Jason Kelce. But his receivers are so good, and Saquon Barkley is a big upgrade too. I would downgrade him a little though as his rushing TD projection maybe went from 10 to seven.
-
AJ Brown didn’t even look like he was running fast as he easily scored a 67-yard TD past the Packers defense. DeVonta Smith seemed to line up more in the slot and was automatic on key third-downs. There was no third receiver of which to speak, and even Dallas Goedert saw only five targets.
-
Barkley looked great, both on his TD catch, and as a rusher. As I said I don’t have any shares despite being high on him initially, but I love Barkley as a player (and bitcoiner!), and still kind of root for him. I hope he smashes this year.
-
-
 @ 3ad01248:962d8a07
2024-10-23 18:59:53
@ 3ad01248:962d8a07
2024-10-23 18:59:53Well I casted my vote early and I didn't vote for Donald Trump or Kamala Harris. I ended up voting for Chase Oliver, the Libertarian candidate for president. Even though I know he has snowball's chance in hell of winning, I simply couldn't bring myself to vote for the two candidates that are pro-war and pro-genocide.
I needed to be able to sleep at night knowing that I did not lend my consent to the mass killing of people in Gaza and around the world using American military equipment to do it. My vote was in protest to the two parties twisted sense of entitlement and delusions of grandeur. The policies that are put in place by these candidates do have an impact on the rest of the world. As much as we would like it not to be the case, it simply is.
So if you are voting for Donald Trump or Kamala Harris you know full well that they represent and what their policies are in regards to foreign policy. When it comes to foreign policy both parties are indistinguishable from each other.
Democrats and Republicans are strong supporters of Israel and will not do anything to stop the genocide occurring there at the moment. The question you have to ask yourself as you step into that voting booth is are you Ok with being complicit in a genocide. Your vote makes you a supporter of this policy. It may sound mean but that's how strongly I feel about this topic.
As Bitcoiners we should want to make the world a better place anyway that we can even if its voting for a candidate that isn't likely going to win. In the long run yes Bitcoin will make situations like this less prevalent but this is a long term goal that isn't going to be achieved today. We must also focus on what we can accomplish in the short term.
Voting for a presidential candidate that believes in free markets and disentangling us from all of these wars and awkward alliances, is in line with the Bitcoin ethos and a step in the right direction. At the end of the day do you want to be able to rest your head at night knowing that you didn't vote for more wars, more killing and more destruction? Is your Bitcoin bag really worth more than your soul and your humanity?
We are here for more than NGU, right? This wasn't an easy decision for me because I understand that Kamala Harris is probably going to be worse for Bitcoin than Donald Trump but at the end of the day I just didn't feel comfortable voting for Trump knowing that he will keep supplying weapons that enable women and children to be wiped off the map.
I urge every Bitcoiner who reads this to look inside yourself and ask what do I stand for and are you willing to sacrifice material wealth to do the right thing? You can't take your Bitcoin with you when you die. Bitcoin will be here long after we are all dead and gone. Tick Toc next block. Life will go on without you being here.
My goal is to be a positive force for good during the little time we have on Earth. I want to believe that most Bitcoiners feels the same way to and will act according to their values.
Bitcoin #Nostr #Politics