-
 @ 8be6bafe:b50da031
2025-02-05 17:00:40
@ 8be6bafe:b50da031
2025-02-05 17:00:40Botev Plovdiv FC is proud to present the Bitcoin Salary Calculator tool, as the foundational tool to showcase athletes the financial power of Bitcoin.
We built the Salary Calculator to help anyone follow in the financial footsteps of prominent athletes such as Kieran Gibbs, Russell Okung, Saquon Barkley, and Renato Moicano, who have significantly increased their savings tank thanks to Bitcoin.
The Bitcoin Salary Calculator allows any person to choose how much of their monthly salary they are comfortable saving in Bitcoin. Instantly, users can backtrack and see how their Bitcoin savings would have performed using the once-in-a-species opportunity which Bitcoin brings.
https://video.nostr.build/a9f2f693f6b5ee75097941e7a30bfc722225918a896b29a73e13e7581dfed77c.mp4
Athletes need Bitcoin more than anyone else
Unlike most people, athletes’ careers and earning years are limited. This has driven the likes of Odell Beckham Jr. and Alex Crognale to also start saving a part of their income in Bitcoin with a long-term outlook as they prepare for retirement.
“The reason why announced 50% of my salary in Bitcoin is because I feel one the noblest things you can do is to get people to understand Bitcoin.” Kieran Gibbs, founder ONE FC, ex Arsenal, ex Inter Miami, ex West Bromich Albion.
“I am trusting Bitcoin for my life after football. Every time my club paid me, I bought Bitcoin.” Alex Crognale, San Antonio FC player.
https://x.com/TFTC21/status/1883228348379533469
“At Botev Plovdiv FC, we believe not only in fostering sporting talent, but also helping them the the most of their careers so they excel in life after retiring from sports. It is with this mission in mind that the club is launching the Bitcoin Football Cup hub, striving to accelerate mass Bitcoin education via sports and athletes - the influencers and role models for billions of people.” shared Botev’s Bitcoin Director George Manolov.
https://x.com/obj/status/1856744340795662432
The Bitcoin Football Cup aims for young prospects to be able to learn key financial lessons from seasoned veterans across all sports. Our Bitcoin Salary Calculator is only the first step toward that goal.
We encourage anyone to hear these stories straight from the current roster of Bitcoin athletes -for whom -in many cases- Bitcoin has allowed them to outperform the wealth it took decades to earn on the field.
Follow us on the Bitcoin Cup’s social media channels to learn more and hear the latest stories of how Bitcoin is shaking up the world of sports:
- Twitter: https://x.com/Bitcoin_Cup/
- Instagram: https://www.instagram.com/BitcoinCup/
- TikTok: https://www.tiktok.com/@BitcoinCup/
- YouTube: https://www.youtube.com/@BitcoinCup/
-
 @ b17fccdf:b7211155
2025-02-01 18:41:27
@ b17fccdf:b7211155
2025-02-01 18:41:27Next new resources about the MiniBolt guide have been released:
- 🆕 Roadmap: LINK
- 🆕 Dynamic Network map: LINK
- 🆕 Nostr community: LINK < ~ REMOVE the "[]" symbols from the URL (naddr...) to access
- 🆕 Linktr FOSS (UC) by Gzuuus: LINK
- 🆕 Donate webpage: 🚾 Clearnet LINK || 🧅 Onion LINK
- 🆕 Contact email: hello@minibolt.info
Enjoy it MiniBolter! 💙
-
 @ b8851a06:9b120ba1
2025-01-28 21:34:54
@ b8851a06:9b120ba1
2025-01-28 21:34:54Private property isn’t lines on dirt or fences of steel—it’s the crystallization of human sovereignty. Each boundary drawn is a silent declaration: This is where my will meets yours, where creation clashes against chaos. What we defend as “mine” or “yours” is no mere object but a metaphysical claim, a scaffold for the unfathomable complexity of voluntary exchange.
Markets breathe only when individuals anchor their choices in the inviolable. Without property, there is no negotiation—only force. No trade—only taking. The deed to land, the title to a car, the seed of an idea: these are not static things but frontiers of being, where human responsibility collides with the infinite permutations of value.
Austrian economics whispers what existentialism shouts: existence precedes essence. Property isn’t granted by systems; it’s asserted through action, defended through sacrifice, and sanctified through mutual recognition. A thing becomes “owned” only when a mind declares it so, and others—through reason or respect—refrain from crossing that unseen line.
Bitcoin? The purest ledger of this truth. A string of code, yes—but one that mirrors the unyielding logic of property itself: scarce, auditable, unconquerable. It doesn’t ask permission. It exists because sovereign minds choose it to.
Sigh. #nostr
I love #Bitcoin. -
 @ 599f67f7:21fb3ea9
2025-01-26 11:01:05
@ 599f67f7:21fb3ea9
2025-01-26 11:01:05¿Qué es Blossom?
nostr:nevent1qqspttj39n6ld4plhn4e2mq3utxpju93u4k7w33l3ehxyf0g9lh3f0qpzpmhxue69uhkummnw3ezuamfdejsygzenanl0hmkjnrq8fksvdhpt67xzrdh0h8agltwt5znsmvzr7e74ywgmr72
Blossom significa Blobs Simply Stored on Media Servers (Blobs Simplemente Almacenados en Servidores de Medios). Blobs son fragmentos de datos binarios, como archivos pero sin nombres. En lugar de nombres, se identifican por su hash sha256. La ventaja de usar hashes sha256 en lugar de nombres es que los hashes son IDs universales que se pueden calcular a partir del archivo mismo utilizando el algoritmo de hash sha256.
💡 archivo -> sha256 -> hash
Blossom es, por lo tanto, un conjunto de puntos finales HTTP que permiten a los usuarios almacenar y recuperar blobs almacenados en servidores utilizando su identidad nostr.
¿Por qué Blossom?
Como mencionamos hace un momento, al usar claves nostr como su identidad, Blossom permite que los datos sean "propiedad" del usuario. Esto simplifica enormemente la cuestión de "qué es spam" para el alojamiento de servidores. Por ejemplo, en nuestro Blossom solo permitimos cargas por miembros de la comunidad verificados que tengan un NIP-05 con nosotros.
Los usuarios pueden subir en múltiples servidores de blossom, por ejemplo, uno alojado por su comunidad, uno de pago, otro público y gratuito, para establecer redundancia de sus datos. Los blobs pueden ser espejados entre servidores de blossom, de manera similar a cómo los relays nostr pueden transmitir eventos entre sí. Esto mejora la resistencia a la censura de blossom.
A continuación se muestra una breve tabla de comparación entre torrents, Blossom y servidores CDN centralizados. (Suponiendo que hay muchos seeders para torrents y se utilizan múltiples servidores con Blossom).
| | Torrents | Blossom | CDN Centralizado | | --------------------------------------------------------------- | -------- | ------- | ---------------- | | Descentralizado | ✅ | ✅ | ❌ | | Resistencia a la censura | ✅ | ✅ | ❌ | | ¿Puedo usarlo para publicar fotos de gatitos en redes sociales? | ❌ | ✅ | ✅ |
¿Cómo funciona?
Blossom utiliza varios tipos de eventos nostr para comunicarse con el servidor de medios.
| kind | descripción | BUD | | ----- | ------------------------------- | ------------------------------------------------------------------ | | 24242 | Evento de autorización | BUD01 | | 10063 | Lista de Servidores de Usuarios | BUD03 |
kind:24242 - Autorización
Esto es esencialmente lo que ya describimos al usar claves nostr como IDs de usuario. En el evento, el usuario le dice al servidor que quiere subir o eliminar un archivo y lo firma con sus claves nostr. El servidor realiza algunas verificaciones en este evento y luego ejecuta el comando del usuario si todo parece estar bien.
kind:10063 - Lista de Servidores de Usuarios
Esto es utilizado por el usuario para anunciar a qué servidores de medios está subiendo. De esta manera, cuando el cliente ve esta lista, sabe dónde subir los archivos del usuario. También puede subir en múltiples servidores definidos en la lista para asegurar redundancia. En el lado de recuperación, si por alguna razón uno de los servidores en la lista del usuario está fuera de servicio, o el archivo ya no se puede encontrar allí, el cliente puede usar esta lista para intentar recuperar el archivo de otros servidores en la lista. Dado que los blobs se identifican por sus hashes, el mismo blob tendrá el mismo hash en cualquier servidor de medios. Todo lo que el cliente necesita hacer es cambiar la URL por la de un servidor diferente.
Ahora, además de los conceptos básicos de cómo funciona Blossom, también hay otros tipos de eventos que hacen que Blossom sea aún más interesante.
| kind | descripción | | ----- | --------------------- | | 30563 | Blossom Drives | | 36363 | Listado de Servidores | | 31963 | Reseña de Servidores |
kind:30563 - Blossom Drives
Este tipo de evento facilita la organización de blobs en carpetas, como estamos acostumbrados con los drives (piensa en Google Drive, iCloud, Proton Drive, etc.). El evento contiene información sobre la estructura de carpetas y los metadatos del drive.
kind:36363 y kind:31963 - Listado y Reseña
Estos tipos de eventos permiten a los usuarios descubrir y reseñar servidores de medios a través de nostr. kind:36363 es un listado de servidores que contiene la URL del servidor. kind:31963 es una reseña, donde los usuarios pueden calificar servidores.
¿Cómo lo uso?
Encuentra un servidor
Primero necesitarás elegir un servidor Blossom donde subirás tus archivos. Puedes navegar por los públicos en blossomservers.com. Algunos de ellos son de pago, otros pueden requerir que tus claves nostr estén en una lista blanca.
Luego, puedes ir a la URL de su servidor y probar a subir un archivo pequeño, como una foto. Si estás satisfecho con el servidor (es rápido y aún no te ha fallado), puedes agregarlo a tu Lista de Servidores de Usuarios. Cubriremos brevemente cómo hacer esto en noStrudel y Amethyst (pero solo necesitas hacer esto una vez, una vez que tu lista actualizada esté publicada, los clientes pueden simplemente recuperarla de nostr).
noStrudel
- Encuentra Relays en la barra lateral, luego elige Servidores de Medios.
- Agrega un servidor de medios, o mejor aún, varios.
- Publica tu lista de servidores. ✅
Amethyst
- En la barra lateral, encuentra Servidores multimedia.
- Bajo Servidores Blossom, agrega tus servidores de medios.
- Firma y publica. ✅
Ahora, cuando vayas a hacer una publicación y adjuntar una foto, por ejemplo, se subirá en tu servidor blossom.
⚠️ Ten en cuenta que debes suponer que los archivos que subas serán públicos. Aunque puedes proteger un archivo con contraseña, esto no ha sido auditado.
Blossom Drive
Como mencionamos anteriormente, podemos publicar eventos para organizar nuestros blobs en carpetas. Esto puede ser excelente para compartir archivos con tu equipo, o simplemente para mantener las cosas organizadas.
Para probarlo, ve a blossom.hzrd149.com (o nuestra instancia comunitaria en blossom.bitcointxoko.com) e inicia sesión con tu método preferido.
Puedes crear una nueva unidad y agregar blobs desde allí.
Bouquet
Si usas múltiples servidores para darte redundancia, Bouquet es una buena manera de obtener una visión general de todos tus archivos. Úsalo para subir y navegar por tus medios en diferentes servidores y sincronizar blobs entre ellos.
Cherry Tree
nostr:nevent1qvzqqqqqqypzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qyghwumn8ghj7mn0wd68ytnhd9hx2tcpzfmhxue69uhkummnw3e82efwvdhk6tcqyp3065hj9zellakecetfflkgudm5n6xcc9dnetfeacnq90y3yxa5z5gk2q6
Cherry Tree te permite dividir un archivo en fragmentos y luego subirlos en múltiples servidores blossom, y más tarde reensamblarlos en otro lugar.
Conclusión
Blossom aún está en desarrollo, pero ya hay muchas cosas interesantes que puedes hacer con él para hacerte a ti y a tu comunidad más soberanos. ¡Pruébalo!
Si deseas mantenerte al día sobre el desarrollo de Blossom, sigue a nostr:nprofile1qyghwumn8ghj7mn0wd68ytnhd9hx2tcpzfmhxue69uhkummnw3e82efwvdhk6tcqyqnxs90qeyssm73jf3kt5dtnk997ujw6ggy6j3t0jjzw2yrv6sy22ysu5ka y dale un gran zap por su excelente trabajo.
Referencias
-
 @ 29af23a9:842ef0c1
2025-01-24 09:28:37
@ 29af23a9:842ef0c1
2025-01-24 09:28:37A Indústria Pornográfica se caracteriza pelo investimento pesado de grandes empresários americanos, desde 2014.
Na década de 90, filmes pornográficos eram feitos às coxas. Era basicamente duas pessoas fazendo sexo amador e sendo gravadas. Não tinha roteiro, nem produção, não tinha maquiagem, nada disso. A distribuição era rudimentar, os assinantes tinham que sair de suas casas, ir até a locadora, sofrer todo tipo de constrangimento para assistir a um filme pornô.
No começo dos anos 2000, o serviço de Pay Per View fez o número de vendas de filmes eróticos (filme erótico é bem mais leve) crescer mas nada se compara com os sites de filmes pornográficos por assinatura.
Com o advento dos serviços de Streaming, os sites que vendem filmes por assinatura se estabeleceram no mercado como nunca foi visto na história.
Hoje, os Produtores usam produtos para esticar os vasos sanguíneos do pênis dos atores e dopam as atrizes para que elas aguentem horas de gravação (a Série Black Mirror fez uma crítica a isso no episódio 1 milhão de méritos de forma sutil).
Além de toda a produção em volta das cenas. Que são gravadas em 4K, para focar bem as partes íntimas dos atores. Quadros fechados, iluminação, tudo isso faz essa Indústria ser "Artística" uma vez que tudo ali é falso. Um filme da Produtora Vixen, por exemplo, onde jovens mulheres transam em mansões com seus empresários estimula o esteriótipo da mina padrão que chama seu chefe rico de "daddy" e seduz ele até ele trair a esposa.
Sites como xvídeos, pornHub e outros nada mais são do que sites que salvam filmes dessas produtoras e hospedam as cenas com anúncios e pop-ups. Alguns sites hospedam o filme inteiro "de graça".
Esse tipo de filme estimula qualquer homem heterosexual com menos de 30 anos, que não tem o córtex frontal de seu cérebro totalmente desenvolvido (segundo estudos só é completamente desenvolvido quando o homem chega aos 31 anos).
A arte Pornográfica faz alguns fantasiarem ter relação sexual com uma gostosa americana branquinha, até escraviza-los. Muitos não conseguem sair do vício e preferem a Ficção à sua esposa real. Então pare de se enganar e admita. A Pornografia faz mal para a saúde mental do homem.
Quem sonha em ter uma transa com Lana Rhodes, deve estar nesse estágio. Trata-se de uma atriz (pornstar) que ganhou muito dinheiro vendendo a ilusão da Arte Pornografica, como a Riley Reid que só gravava para grandes Produtoras. Ambas se arrependeram da carreira artística e agora tentam viver suas vidas como uma mulher comum.
As próprias atrizes se consideram artistas, como Mia Malkova, chegou a dizer que Pornografia é a vida dela, que é "Lindo e Sofisticado."
Mia Malkova inclusive faz questão de dizer que a industria não escravisa mulheres jovens. Trata-se de um negócio onde a mulher assina um contrato com uma produtora e recebe um cachê por isso. Diferente do discurso da Mia Khalifa em entrevista para a BBC, onde diz que as mulheres são exploradas por homens poderosos. Vai ela está confundindo o Conglomerado Vixen com a Rede Globo ou com a empresa do Harvey Weinstein.
Enfim, se você é um homem solteiro entre 18 e 40 anos que já consumiu ou que ainda consome pornografia, sabia que sofrerá consequências. Pois trata-se de "produções artísticas" da indústria audiovisual que altera os níveis de dopamina do seu cérebro, mudando a neuroplasticidade e diminuindo a massa cinzenta, deixando o homem com memória fraca, sem foco e com mente nebulosa.
Por que o Estado não proíbe/criminaliza a Pornografia se ela faz mal? E desde quando o Estado quer o nosso bem? Existem grandes empresarios que financiam essa indústria ajudando governos a manterem o povo viciado e assim alienado. É um pão e circo, só que muito mais viciante e maléfico. Eu costume dizer aos meus amigos que existem grandes empresários jvdeus que são donos de grandes Produtoras de filmes pornográficos como o Conglomerado Vixen. Então se eles assistem vídeos pirateados de filmes dessas produtoras, eles estão no colo do Judeu.
-
 @ 83279ad2:bd49240d
2025-01-24 09:15:37
@ 83279ad2:bd49240d
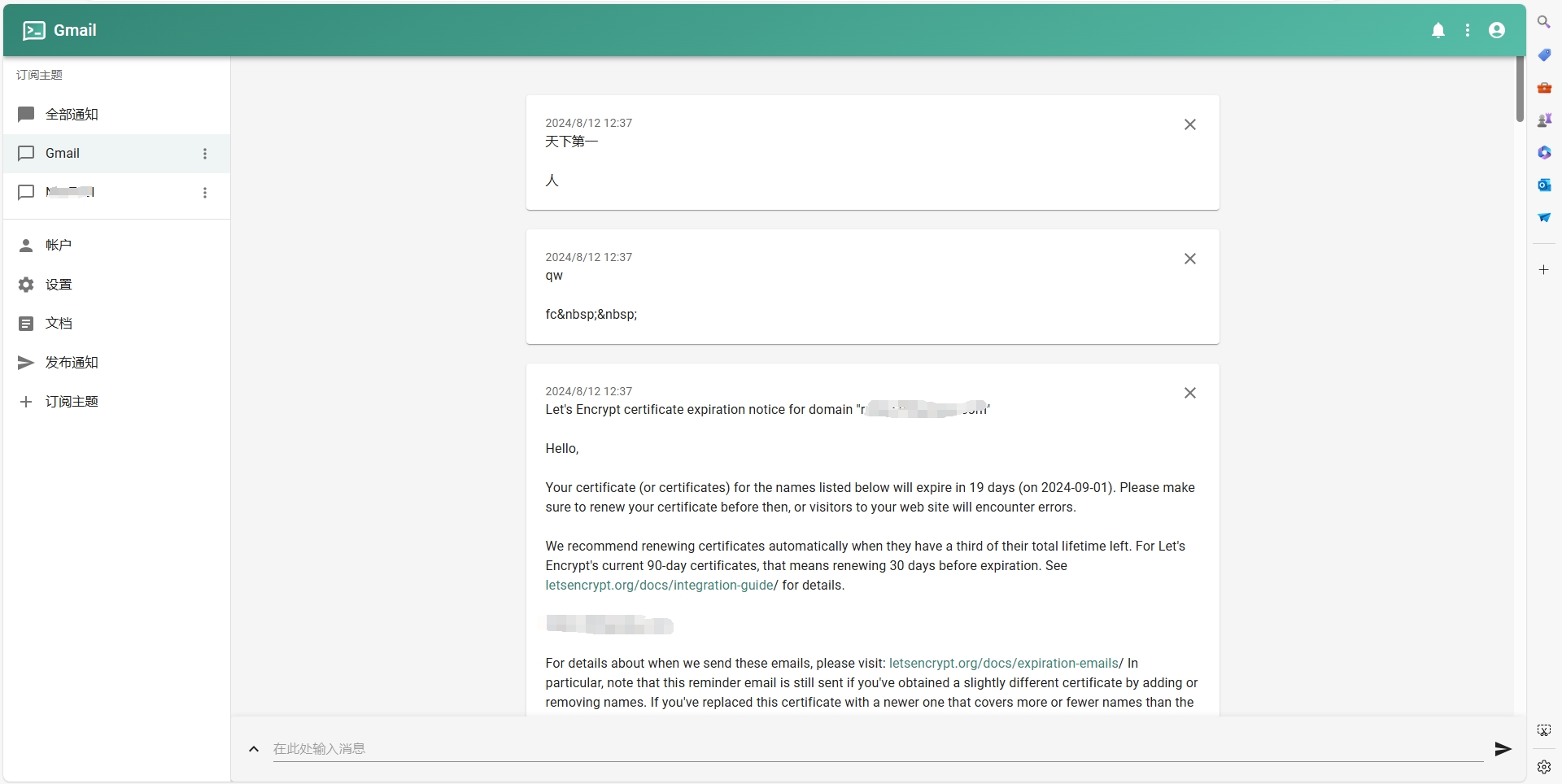
2025-01-24 09:15:37備忘録として書きます。意外と時間がかかりました。全体で1時間くらいかかるので気長にやりましょう。 仮想通貨取引所(販売所ではないので、玄人が使えばお得らしい)かつBitcoinの送金手数料が無料(全ての取引所が無料ではない、例えばbitbankは0.0006bitcoinかかる)なので送金元はGMOコインを使います。(注意:GMOコインは0.02ビットコイン以下は全額送金になってしまいます) 今回はカストディアルウォレットのWallet of Satoshiに送金します。 以下手順 1. GMOコインでbitcoinを買います。 2. GMOコインの左のタブから入出金 暗号資産を選択します。 3. 送付のタブを開いて、+新しい宛先を追加するを選択します。 4. 送付先:GMOコイン以外、送付先ウォレット:プライベートウォレット(MetaMaskなど)、受取人:ご本人さま を選んで宛先情報の登録を選ぶと次の画面になります。
 5. 宛先名称にwallet of satoshi(これはなんでも良いです わかりやすい名称にしましょう) wallet of satoshiを開いて、受信→Bitcoin On-Chainからアドレスをコピーして、ビットコインアドレスに貼り付けます。
5. 宛先名称にwallet of satoshi(これはなんでも良いです わかりやすい名称にしましょう) wallet of satoshiを開いて、受信→Bitcoin On-Chainからアドレスをコピーして、ビットコインアドレスに貼り付けます。 6. 登録するを押します。これで送金先の登録ができました。GMOコインの審査がありますがすぐ終わると思います。
7. ここから送金をします。送付のタブから登録したビットコインの宛先リストwallet of satoshiを選択し、送付数量と送付目的を選択して、2段階認証をします。
6. 登録するを押します。これで送金先の登録ができました。GMOコインの審査がありますがすぐ終わると思います。
7. ここから送金をします。送付のタブから登録したビットコインの宛先リストwallet of satoshiを選択し、送付数量と送付目的を選択して、2段階認証をします。 8. 実行を押せば終わりです。もうあなたがやることはありません。送金が終わるのを40分くらい眺めるだけです。
8. 実行を押せば終わりです。もうあなたがやることはありません。送金が終わるのを40分くらい眺めるだけです。 8. 取引履歴のタブから今の送金のステータスが見れます。
8. 取引履歴のタブから今の送金のステータスが見れます。 9. 15分くらい待つとステータスが受付に変わります。
9. 15分くらい待つとステータスが受付に変わります。 10. 20分くらい待つとトランザクションIDが表示されます。
10. 20分くらい待つとトランザクションIDが表示されます。

この時点からwallet of satoshiにも送金されていることが表示されます。(まだ完了はしていない)
 11. ステータスが完了になったら送金終わりです。
11. ステータスが完了になったら送金終わりです。

wallet of satoshiにも反映されます。

お疲れ様でした!
-
 @ b17fccdf:b7211155
2025-01-21 18:33:28
@ b17fccdf:b7211155
2025-01-21 18:33:28
CHECK OUT at ~ > ramix.minibolt.info < ~
Main changes:
- Adapted to Raspberry Pi 5, with the possibility of using internal storage: a PCIe to M.2 adapter + SSD NVMe:
Connect directly to the board, remove the instability issues with the USB connection, and unlock the ability to enjoy higher transfer speeds**
- Based on Debian 12 (Raspberry Pi OS Bookworm - 64-bit).
- Updated all services that have been tested until now, to the latest version.
- Same as the MiniBolt guide, changed I2P, Fulcrum, and ThunderHub guides, to be part of the core guide.
- All UI & UX improvements in the MiniBolt guide are included.
- Fix some links and wrong command issues.
- Some existing guides have been improved to clarify the following steps.
Important notes:
- The RRSS will be the same as the MiniBolt original project (for now) | More info -> HERE <-
- The common resources like the Roadmap or Networkmap have been merged and will be used together | Check -> HERE <-
- The attempt to upgrade from Bullseye to Bookworm (RaspiBolt to RaMiX migration) has failed due to several difficult-to-resolve dependency conflicts, so unfortunately, there will be no dedicated migration guide and only the possibility to start from scratch ☹️
⚠️ Attention‼️-> This guide is in the WIP (work in progress) state and hasn't been completely tested yet. Many steps may be incorrect. Pay special attention to the "Status: Not tested on RaMiX" tag at the beginning of the guides. Be careful and act behind your responsibility.
For Raspberry Pi lovers!❤️🍓
Enjoy it RaMiXer!! 💜
By ⚡2FakTor⚡ for the plebs with love ❤️🫂
- Adapted to Raspberry Pi 5, with the possibility of using internal storage: a PCIe to M.2 adapter + SSD NVMe:
-
 @ 7f29628d:e160cccc
2025-01-07 11:50:30
@ 7f29628d:e160cccc
2025-01-07 11:50:30Der gut informierte Bürger denkt bei der Pandemie sofort an Intensivstationen, an die Bilder aus Bergamo und erinnert sich an die Berichterstattung damals – also muss es wohl ein Maximum gewesen sein. Manche Skeptiker behaupten jedoch das Gegenteil. Klarheit sollte ein Blick nach Wiesbaden, zum Statistischen Bundesamt, schaffen. Schließlich sitzen dort gut bezahlte Profis, die seit vielen Jahrzehnten die Sterbestatistik pflegen und veröffentlichen. Jeder Todesfall wird in Deutschland über die Standesämter exakt erfasst.
Doch die Überraschung: Das Statistische Bundesamt liefert uns auf diese einfache Frage zwei extrem unterschiedliche Antworten – ein Minimum und ein Maximum. Das Ergebnis hängt davon ab, wie tief man in die Veröffentlichungen des Bundesamtes eintaucht. Betrachtet man nur die Webseiten und Pressemitteilungen, erhält man den Eindruck eines Maximums. Schaut man jedoch etwas tiefer in die Tabellen und Rohdaten, zeigt sich plötzlich ein Minimum. Aber wie kann das sein? Beides gleichzeitig geht ja wohl kaum. Wer lügt hier – die Tabellen des Amtes oder die Pressemitteilungen? Gehen wir dieser Frage Schritt für Schritt auf den Grund.
2020: Ein historisches Maximum?
Schauen wir uns die vielen Hundert Veröffentlichungen des Statistischen Bundesamtes aus dieser Zeit an. Oder wir kürzen ab und fragen ChatGPT, da die KI auf diesen Daten trainiert wurde und das gesamte Material kennt. Die Frage an ChatGPT lautet also: Wie war das Sterbegeschehen im Jahr 2020 im Vergleich zu den Vorjahren?
ChatGPT antwortet: »Im Jahr 2020 war die Sterblichkeit in Deutschland höher als in den Jahren zuvor. Es gab eine Übersterblichkeit von etwa 982.000 Todesfällen, das sind rund 46.000 mehr als der Durchschnitt der Vorjahre (2016 bis 2019). Dieser Anstieg wurde überwiegend im Zusammenhang mit der COVID-19-Pandemie gesehen. Während die Sterbezahlen in den Vorjahren schwankten, war ein solch signifikanter Anstieg wie 2020 bisher nicht zu beobachten.«
Wir fragen konkreter: Ist es ein Fakt, dass wir eine so ernste Lage im Sterbegeschehen wie im Frühjahr 2020 noch nie erlebt haben?
ChatGPT bestätigt: »Ja, die COVID-19-Pandemie führte im Frühjahr 2020 zu einer außergewöhnlichen Situation im Sterbegeschehen in Deutschland. Die dramatische Übersterblichkeit, die ab der 13. Kalenderwoche auftrat, veranlasste das Statistische Bundesamt, besonders eindringliche Warnungen zu veröffentlichen. Der damalige Vizepräsident des Amtes und andere führende Stimmen wiesen öffentlich darauf hin, dass die Todesfallzahlen stark vom Durchschnitt abwichen. Diese klare Warnung richtete sich an die Öffentlichkeit und die Politik gleichermaßen. Die Medien berichteten intensiv über diese Warnungen, was das Bewusstsein für die Schwere der Pandemie erheblich schärfte. In den vergangenen Jahrzehnten hatte es keine vergleichbare Übersterblichkeit gegeben, die eine solch umfangreiche Kommunikation durch das Statistische Bundesamt erforderlich gemacht hätte.«
Ein gut informierter Zeitungsleser wird sich an dieser Stelle bestätigt fühlen: Ja, so war es damals. Ein Maximum im Sterbegeschehen – wegen der Pandemie. Oder etwa nicht?
2020: Ein historisches Minimum?
Tauchen wir in die Rohdaten des Statistischen Bundesamtes ein. Die Tabellen, die das Amt seit Jahrzehnten verlässlich veröffentlicht, nennen sich Sterbetafeln. Diese werden jährlich bereitgestellt und stehen auf der Website des Bundesamtes zum Download bereit. Ein erster Blick in die Sterbetafeln mag den Laien abschrecken, doch mit einer kurzen Erklärung wird alles verständlich. Wir gehen schrittweise vor.
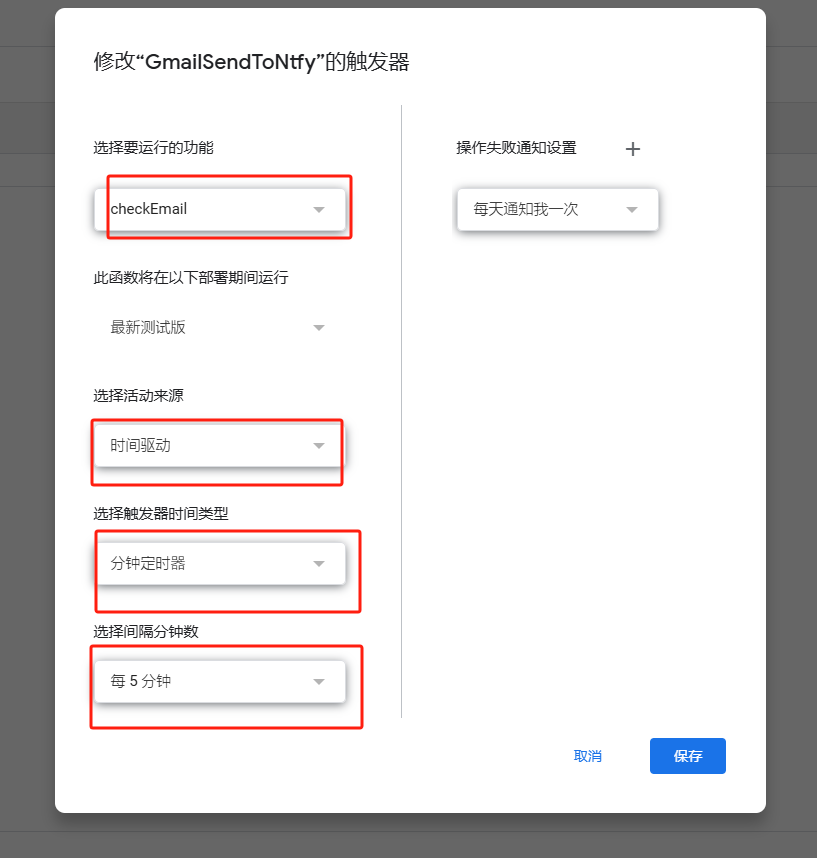
Nehmen wir die Sterbetafel des Jahres 2017. Sie enthält zwei große Tabellen – eine für Männer und eine für Frauen. Jede Zeile der Tabelle steht für einen Jahrgang, zum Beispiel zeigt die Zeile 79 die Daten der 79-jährigen Männer. Besonders wichtig ist nun die zweite Spalte, in der der Wert 0,05 eingetragen ist. Das bedeutet, dass 5 Prozent der 79-jährigen Männer im Jahr 2017 verstorben sind. Das ist die wichtige Kennzahl. Wenn wir diesen exakten Wert, den man auch als Sterberate bezeichnet, nun in ein Säulendiagramm eintragen, erhalten wir eine leicht verständliche visuelle Darstellung (Grafik 1).
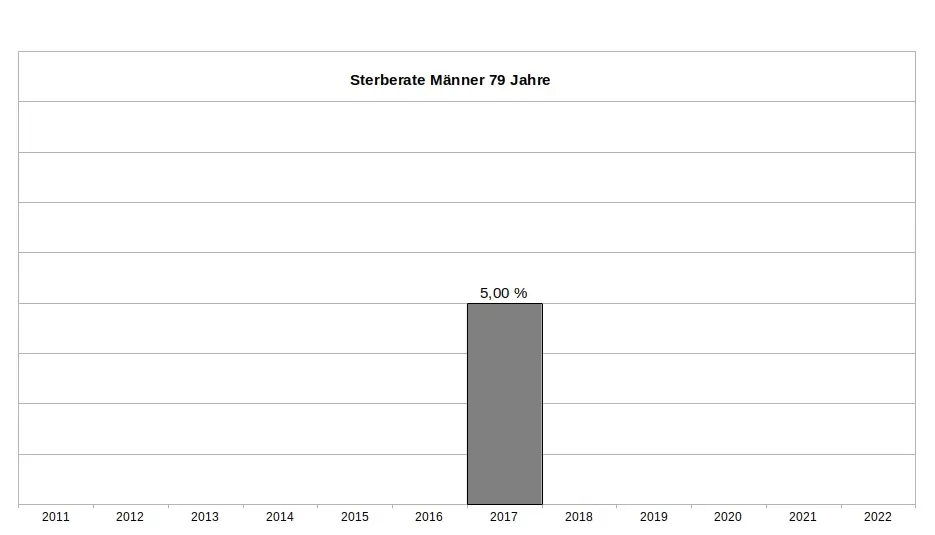
Es ist wichtig zu betonen, dass dieser Wert weder ein Schätzwert noch eine Modellrechnung oder Prognose ist, sondern ein exakter Messwert, basierend auf einer zuverlässigen Zählung. Sterberaten (für die Fachleute auch Sterbewahrscheinlichkeiten qx) sind seit Johann Peter Süßmilch (1707–1767) der Goldstandard der Sterbestatistik. Jeder Aktuar wird das bestätigen. Fügen wir nun die Sterberaten der 79-jährigen Männer aus den Jahren davor und danach hinzu, um das Gesamtbild zu sehen (Grafik 2). Und nun die entscheidende Frage: Zeigt das Jahr 2020 ein Maximum oder ein Minimum?
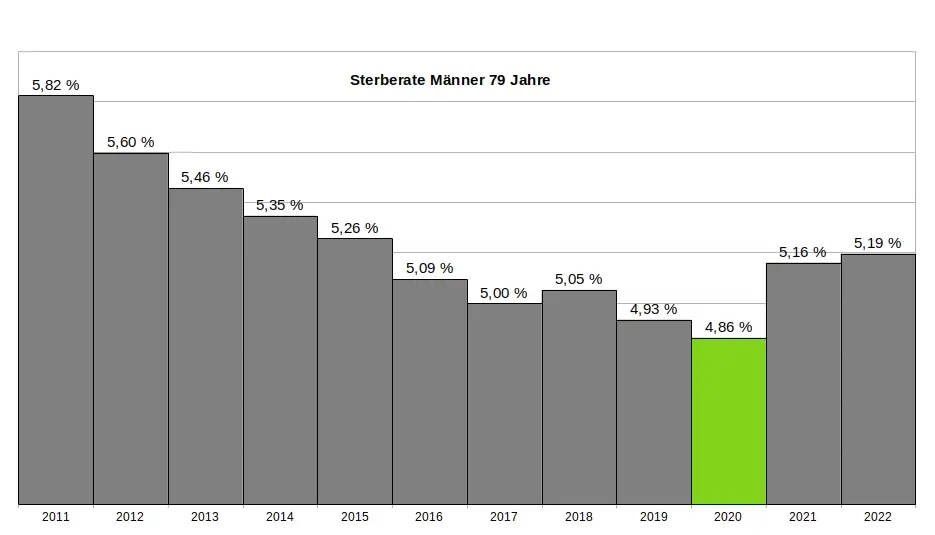
Ein kritischer Leser könnte vermuten, dass die 79-jährigen Männer eine Ausnahme darstellen und andere Jahrgänge im Jahr 2020 ein Maximum zeigen würden. Doch das trifft nicht zu. Kein einziger Jahrgang verzeichnete im Jahr 2020 ein Maximum. Im Gegenteil: Auch die 1-Jährigen, 2-Jährigen, 3-Jährigen, 9-Jährigen, 10-Jährigen, 15-Jährigen, 18-Jährigen und viele weitere männliche Jahrgänge hatten ihr Minimum im Jahr 2020. Dasselbe gilt bei den Frauen. Insgesamt hatten 31 Jahrgänge ihr Minimum im Jahr 2020. Wenn wir schließlich alle Jahrgänge in einer einzigen Grafik zusammenfassen, ergibt sich ein klares Bild: Das Minimum im Sterbegeschehen lag im Jahr 2020 (Grafik 3).
Ein kritischer Leser könnte nun wiederum vermuten, dass es innerhalb des Jahres 2020 möglicherweise starke Ausschläge nach oben bei einzelnen Jahrgängen gegeben haben könnte, die später durch Ausschläge nach unten ausgeglichen wurden – und dass diese Schwankungen in der jährlichen Übersicht nicht sichtbar sind. Doch auch das trifft nicht zu. Ein Blick auf die wöchentlichen Sterberaten zeigt, dass die ersten acht Monate der Pandemie keine nennenswerten Auffälligkeiten aufweisen. Es bleibt dabei: Die Rohdaten des Statistischen Bundesamtes bestätigen zweifelsfrei, dass die ersten acht Monate der Pandemie das historische Minimum im Sterbegeschehen darstellen. (Für die Fachleute sei angemerkt, dass im gleichen Zeitraum die Lebenserwartung die historischen Höchststände erreicht hatte – Grafik 4.)
So konstruierte das Amt aus einem Minimum ein Maximum:
Zur Erinnerung: Die Rohdaten des Statistischen Bundesamtes, die in den jährlichen Sterbetafeln zweifelsfrei dokumentiert sind, zeigen für das Jahr 2020 eindeutig ein Minimum im Sterbegeschehen. Aus diesen »in Stein gemeißelten« Zahlen ein Maximum zu »konstruieren«, ohne die Rohdaten selbst zu verändern, scheint auf den ersten Blick eine unlösbare Aufgabe. Jeder Student würde an einer solchen Herausforderung scheitern. Doch das Statistische Bundesamt hat einen kreativen Weg gefunden - ein Meisterstück gezielter Manipulation. In fünf Schritten zeigt sich, wie diese Täuschung der Öffentlichkeit umgesetzt wurde:
(1) Ignorieren der Sterberaten: Die präzisen, objektiven und leicht verständlichen Sterberaten aus den eigenen Sterbetafeln wurden konsequent ignoriert und verschwiegen. Diese Daten widersprachen dem gewünschten Narrativ und wurden daher gezielt ausgeklammert.
(2) Fokus auf absolute Todeszahlen: Die Aufmerksamkeit wurde stattdessen auf die absolute Zahl der Todesfälle gelenkt. Diese wirkt allein durch ihre schiere Größe dramatisch und emotionalisiert die Diskussion. Ein entscheidender Faktor wurde dabei ignoriert: Die absolute Zahl der Todesfälle steigt aufgrund der demografischen Entwicklung jedes Jahr an. Viele Menschen verstehen diesen Zusammenhang nicht und verbinden die steigenden Zahlen fälschlicherweise mit der vermeintlichen Pandemie.
(3) Einführung der Übersterblichkeit als neue Kennzahl: Erst ab Beginn der „Pandemie“ wurde die Kennzahl "Übersterblichkeit" eingeführt – und dies mit einer fragwürdigen Methode, die systematisch überhöhte Werte lieferte. Diese Kennzahl wurde regelmäßig, oft monatlich oder sogar wöchentlich, berechnet und diente als ständige Grundlage für alarmierende Schlagzeilen.
(4) Intensive Öffentlichkeitsarbeit: Durch eine breit angelegte Kampagne wurden die manipulativen Kennzahlen gezielt in den Fokus gerückt. Pressemitteilungen, Podcasts und öffentliche Auftritte konzentrierten sich fast ausschließlich auf die absoluten Todeszahlen und die Übersterblichkeit. Ziel war es, den Eindruck einer dramatischen Situation in der Öffentlichkeit zu verstärken.
(5) Bekämpfen kritischer Stimmen: Kritiker, die die Schwächen und manipulativen Aspekte dieser Methoden aufdeckten, wurden systematisch diskreditiert. Ihre Glaubwürdigkeit und Kompetenz wurden öffentlich infrage gestellt, um das sorgsam konstruierte Narrativ zu schützen.
Ohne diesen begleitenden Statistik-Betrug wäre das gesamte Pandemie-Theater meiner Meinung nach nicht möglich gewesen. Wer aus einem faktischen Minimum ein scheinbares Maximum "erschafft", handelt betrügerisch. Die Folgen dieses Betruges sind gravierend. Denken wir an die Angst, die in der Bevölkerung geschürt wurde – die Angst, bald sterben zu müssen. Denken wir an Masken, Abstandsregeln, isolierte ältere Menschen, Kinderimpfungen und all die Maßnahmen, die unter anderem auf diese falsche Statistik zurückgehen.
Wollen wir Bürger uns das gefallen lassen?
Wenn wir als Bürger zulassen, dass ein derart offensichtlicher und nachprüfbarer Täuschungsversuch ohne Konsequenzen bleibt, dann gefährdet das nicht nur die Integrität unserer Institutionen – es untergräbt das Fundament unserer Gesellschaft. In der DDR feierte man öffentlich Planerfüllung und Übererfüllung, während die Regale leer blieben. Damals wusste jeder: Statistik war ein Propagandainstrument. Niemand traute den Zahlen, die das Staatsfernsehen verkündete.
Während der Pandemie war es anders. Die Menschen vertrauten den Mitteilungen des Statistischen Bundesamtes und des RKI – blind. Die Enthüllungen durch den "RKI-Leak" haben gezeigt, dass auch das Robert-Koch-Institut nicht der Wissenschaft, sondern den Weisungen des Gesundheitsministers und militärischen Vorgaben folgte. Warum sollte es beim Statistischen Bundesamt anders gewesen sein? Diese Behörde ist dem Innenministerium unterstellt und somit ebenfalls weisungsgebunden.
Die Beweise für Täuschung liegen offen zutage. Es braucht keinen Whistleblower, keine geheimen Enthüllungen: Die Rohdaten des Statistischen Bundesamtes sprechen für sich. Sie sind öffentlich einsehbar – klar und unmissverständlich. Die Daten, die Tabellen, die Veröffentlichungen des Amtes selbst – sie sind die Anklageschrift. Sie zeigen, was wirklich war. Nicht mehr und nicht weniger.
Und wir? Was tun wir? Schweigen wir? Oder fordern wir endlich ein, was unser Recht ist? Wir Bürger dürfen das nicht hinnehmen. Es ist Zeit, unsere Behörden zur Rechenschaft zu ziehen. Diese Institutionen arbeiten nicht für sich – sie arbeiten für uns. Wir finanzieren sie, und wir haben das Recht, Transparenz und Verantwortung einzufordern. Manipulationen wie diese müssen aufgearbeitet werden und dürfen nie wieder geschehen. Die Strukturen, die solche Fehlentwicklungen in unseren Behörden ermöglicht haben, müssen offengelegt werden. Denn eine Demokratie lebt von Vertrauen – und Vertrauen muss verdient werden. Jeden Tag aufs Neue.
.
.
MARCEL BARZ, Jahrgang 1975, war Offizier der Bundeswehr und studierte Wirtschafts- und Organisationswissenschaften sowie Wirtschaftsinformatik. Er war Gründer und Geschäftsführer einer Softwarefirma, die sich auf Datenanalyse und Softwareentwicklung spezialisiert hatte. Im August 2021 veröffentlichte Barz den Videovortrag »Die Pandemie in den Rohdaten«, der über eine Million Aufrufe erzielte. Seitdem macht er als "Erbsenzähler" auf Widersprüche in amtlichen Statistiken aufmerksam.
-
 @ eac63075:b4988b48
2025-01-04 19:41:34
@ eac63075:b4988b48
2025-01-04 19:41:34Since its creation in 2009, Bitcoin has symbolized innovation and resilience. However, from time to time, alarmist narratives arise about emerging technologies that could "break" its security. Among these, quantum computing stands out as one of the most recurrent. But does quantum computing truly threaten Bitcoin? And more importantly, what is the community doing to ensure the protocol remains invulnerable?
The answer, contrary to sensationalist headlines, is reassuring: Bitcoin is secure, and the community is already preparing for a future where quantum computing becomes a practical reality. Let’s dive into this topic to understand why the concerns are exaggerated and how the development of BIP-360 demonstrates that Bitcoin is one step ahead.
What Is Quantum Computing, and Why Is Bitcoin Not Threatened?
Quantum computing leverages principles of quantum mechanics to perform calculations that, in theory, could exponentially surpass classical computers—and it has nothing to do with what so-called “quantum coaches” teach to scam the uninformed. One of the concerns is that this technology could compromise two key aspects of Bitcoin’s security:
- Wallets: These use elliptic curve algorithms (ECDSA) to protect private keys. A sufficiently powerful quantum computer could deduce a private key from its public key.
- Mining: This is based on the SHA-256 algorithm, which secures the consensus process. A quantum attack could, in theory, compromise the proof-of-work mechanism.
Understanding Quantum Computing’s Attack Priorities
While quantum computing is often presented as a threat to Bitcoin, not all parts of the network are equally vulnerable. Theoretical attacks would be prioritized based on two main factors: ease of execution and potential reward. This creates two categories of attacks:
1. Attacks on Wallets
Bitcoin wallets, secured by elliptic curve algorithms, would be the initial targets due to the relative vulnerability of their public keys, especially those already exposed on the blockchain. Two attack scenarios stand out:
-
Short-term attacks: These occur during the interval between sending a transaction and its inclusion in a block (approximately 10 minutes). A quantum computer could intercept the exposed public key and derive the corresponding private key to redirect funds by creating a transaction with higher fees.
-
Long-term attacks: These focus on old wallets whose public keys are permanently exposed. Wallets associated with Satoshi Nakamoto, for example, are especially vulnerable because they were created before the practice of using hashes to mask public keys.
We can infer a priority order for how such attacks might occur based on urgency and importance.
 Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)
Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)2. Attacks on Mining
Targeting the SHA-256 algorithm, which secures the mining process, would be the next objective. However, this is far more complex and requires a level of quantum computational power that is currently non-existent and far from realization. A successful attack would allow for the recalculation of all possible hashes to dominate the consensus process and potentially "mine" it instantly.
 Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin Attacks
Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin AttacksRecently, Narcelio asked me about a statement I made on Tubacast:
https://x.com/eddieoz/status/1868371296683511969
If an attack became a reality before Bitcoin was prepared, it would be necessary to define the last block prior to the attack and proceed from there using a new hashing algorithm. The solution would resemble the response to the infamous 2013 bug. It’s a fact that this would cause market panic, and Bitcoin's price would drop significantly, creating a potential opportunity for the well-informed.
Preferably, if developers could anticipate the threat and had time to work on a solution and build consensus before an attack, they would simply decide on a future block for the fork, which would then adopt the new algorithm. It might even rehash previous blocks (reaching consensus on them) to avoid potential reorganization through the re-mining of blocks using the old hash. (I often use the term "shielding" old transactions).
How Can Users Protect Themselves?
While quantum computing is still far from being a practical threat, some simple measures can already protect users against hypothetical scenarios:
- Avoid using exposed public keys: Ensure funds sent to old wallets are transferred to new ones that use public key hashes. This reduces the risk of long-term attacks.
- Use modern wallets: Opt for wallets compatible with SegWit or Taproot, which implement better security practices.
- Monitor security updates: Stay informed about updates from the Bitcoin community, such as the implementation of BIP-360, which will introduce quantum-resistant addresses.
- Do not reuse addresses: Every transaction should be associated with a new address to minimize the risk of repeated exposure of the same public key.
- Adopt secure backup practices: Create offline backups of private keys and seeds in secure locations, protected from unauthorized access.
BIP-360 and Bitcoin’s Preparation for the Future
Even though quantum computing is still beyond practical reach, the Bitcoin community is not standing still. A concrete example is BIP-360, a proposal that establishes the technical framework to make wallets resistant to quantum attacks.
BIP-360 addresses three main pillars:
- Introduction of quantum-resistant addresses: A new address format starting with "BC1R" will be used. These addresses will be compatible with post-quantum algorithms, ensuring that stored funds are protected from future attacks.
- Compatibility with the current ecosystem: The proposal allows users to transfer funds from old addresses to new ones without requiring drastic changes to the network infrastructure.
- Flexibility for future updates: BIP-360 does not limit the choice of specific algorithms. Instead, it serves as a foundation for implementing new post-quantum algorithms as technology evolves.
This proposal demonstrates how Bitcoin can adapt to emerging threats without compromising its decentralized structure.
Post-Quantum Algorithms: The Future of Bitcoin Cryptography
The community is exploring various algorithms to protect Bitcoin from quantum attacks. Among the most discussed are:
- Falcon: A solution combining smaller public keys with compact digital signatures. Although it has been tested in limited scenarios, it still faces scalability and performance challenges.
- Sphincs: Hash-based, this algorithm is renowned for its resilience, but its signatures can be extremely large, making it less efficient for networks like Bitcoin’s blockchain.
- Lamport: Created in 1977, it’s considered one of the earliest post-quantum security solutions. Despite its reliability, its gigantic public keys (16,000 bytes) make it impractical and costly for Bitcoin.
Two technologies show great promise and are well-regarded by the community:
- Lattice-Based Cryptography: Considered one of the most promising, it uses complex mathematical structures to create systems nearly immune to quantum computing. Its implementation is still in its early stages, but the community is optimistic.
- Supersingular Elliptic Curve Isogeny: These are very recent digital signature algorithms and require extensive study and testing before being ready for practical market use.
The final choice of algorithm will depend on factors such as efficiency, cost, and integration capability with the current system. Additionally, it is preferable that these algorithms are standardized before implementation, a process that may take up to 10 years.
Why Quantum Computing Is Far from Being a Threat
The alarmist narrative about quantum computing overlooks the technical and practical challenges that still need to be overcome. Among them:
- Insufficient number of qubits: Current quantum computers have only a few hundred qubits, whereas successful attacks would require millions.
- High error rate: Quantum stability remains a barrier to reliable large-scale operations.
- High costs: Building and operating large-scale quantum computers requires massive investments, limiting their use to scientific or specific applications.
Moreover, even if quantum computers make significant advancements, Bitcoin is already adapting to ensure its infrastructure is prepared to respond.
Conclusion: Bitcoin’s Secure Future
Despite advancements in quantum computing, the reality is that Bitcoin is far from being threatened. Its security is ensured not only by its robust architecture but also by the community’s constant efforts to anticipate and mitigate challenges.
The implementation of BIP-360 and the pursuit of post-quantum algorithms demonstrate that Bitcoin is not only resilient but also proactive. By adopting practical measures, such as using modern wallets and migrating to quantum-resistant addresses, users can further protect themselves against potential threats.
Bitcoin’s future is not at risk—it is being carefully shaped to withstand any emerging technology, including quantum computing.
-
 @ f9cf4e94:96abc355
2024-12-31 20:18:59
@ f9cf4e94:96abc355
2024-12-31 20:18:59Scuttlebutt foi iniciado em maio de 2014 por Dominic Tarr ( dominictarr ) como uma rede social alternativa off-line, primeiro para convidados, que permite aos usuários obter controle total de seus dados e privacidade. Secure Scuttlebutt (ssb) foi lançado pouco depois, o que coloca a privacidade em primeiro plano com mais recursos de criptografia.
Se você está se perguntando de onde diabos veio o nome Scuttlebutt:
Este termo do século 19 para uma fofoca vem do Scuttlebutt náutico: “um barril de água mantido no convés, com um buraco para uma xícara”. A gíria náutica vai desde o hábito dos marinheiros de se reunir pelo boato até a fofoca, semelhante à fofoca do bebedouro.

Marinheiros se reunindo em torno da rixa. ( fonte )
Dominic descobriu o termo boato em um artigo de pesquisa que leu.
Em sistemas distribuídos, fofocar é um processo de retransmissão de mensagens ponto a ponto; as mensagens são disseminadas de forma análoga ao “boca a boca”.
Secure Scuttlebutt é um banco de dados de feeds imutáveis apenas para acréscimos, otimizado para replicação eficiente para protocolos ponto a ponto. Cada usuário tem um log imutável somente para acréscimos no qual eles podem gravar. Eles gravam no log assinando mensagens com sua chave privada. Pense em um feed de usuário como seu próprio diário de bordo, como um diário de bordo (ou diário do capitão para os fãs de Star Trek), onde eles são os únicos autorizados a escrever nele, mas têm a capacidade de permitir que outros amigos ou colegas leiam ao seu diário de bordo, se assim o desejarem.
Cada mensagem possui um número de sequência e a mensagem também deve fazer referência à mensagem anterior por seu ID. O ID é um hash da mensagem e da assinatura. A estrutura de dados é semelhante à de uma lista vinculada. É essencialmente um log somente de acréscimo de JSON assinado. Cada item adicionado a um log do usuário é chamado de mensagem.
Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.

Perspectivas dos participantes
Scuttlebot
O software Pub é conhecido como servidor Scuttlebutt (servidor ssb ), mas também é conhecido como “Scuttlebot” e
sbotna linha de comando. O servidor SSB adiciona comportamento de rede ao banco de dados Scuttlebutt (SSB). Estaremos usando o Scuttlebot ao longo deste tutorial.Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.


Perspectivas dos participantes
Pubs - Hubs
Pubs públicos
| Pub Name | Operator | Invite Code | | ------------------------------------------------------------ | ------------------------------------------------------------ | ------------------------------------------------------------ | |
scuttle.us| @Ryan |scuttle.us:8008:@WqcuCOIpLtXFRw/9vOAQJti8avTZ9vxT9rKrPo8qG6o=.ed25519~/ZUi9Chpl0g1kuWSrmehq2EwMQeV0Pd+8xw8XhWuhLE=| | pub1.upsocial.com | @freedomrules |pub1.upsocial.com:8008:@gjlNF5Cyw3OKZxEoEpsVhT5Xv3HZutVfKBppmu42MkI=.ed25519~lMd6f4nnmBZEZSavAl4uahl+feajLUGqu8s2qdoTLi8=| | Monero Pub | @Denis |xmr-pub.net:8008:@5hTpvduvbDyMLN2IdzDKa7nx7PSem9co3RsOmZoyyCM=.ed25519~vQU+r2HUd6JxPENSinUWdfqrJLlOqXiCbzHoML9iVN4=| | FreeSocial | @Jarland |pub.freesocial.co:8008:@ofYKOy2p9wsaxV73GqgOyh6C6nRGFM5FyciQyxwBd6A=.ed25519~ye9Z808S3KPQsV0MWr1HL0/Sh8boSEwW+ZK+8x85u9w=| |ssb.vpn.net.br| @coffeverton |ssb.vpn.net.br:8008:@ze8nZPcf4sbdULvknEFOCbVZtdp7VRsB95nhNw6/2YQ=.ed25519~D0blTolH3YoTwSAkY5xhNw8jAOjgoNXL/+8ZClzr0io=| | gossip.noisebridge.info | Noisebridge Hackerspace @james.network |gossip.noisebridge.info:8008:@2NANnQVdsoqk0XPiJG2oMZqaEpTeoGrxOHJkLIqs7eY=.ed25519~JWTC6+rPYPW5b5zCion0gqjcJs35h6JKpUrQoAKWgJ4=|Pubs privados
Você precisará entrar em contato com os proprietários desses bares para receber um convite.
| Pub Name | Operator | Contact | | --------------------------------------------- | ------------------------------------------------------------ | ----------------------------------------------- | |
many.butt.nz| @dinosaur | mikey@enspiral.com | |one.butt.nz| @dinosaur | mikey@enspiral.com | |ssb.mikey.nz| @dinosaur | mikey@enspiral.com | | ssb.celehner.com | @cel | cel@celehner.com |Pubs muito grandes
Aviso: embora tecnicamente funcione usar um convite para esses pubs, você provavelmente se divertirá se o fizer devido ao seu tamanho (muitas coisas para baixar, risco para bots / spammers / idiotas)
| Pub Name | Operator | Invite Code | | --------------------------------------- | ----------------------------------------------- | ------------------------------------------------------------ | |
scuttlebutt.de| SolSoCoG |scuttlebutt.de:8008:@yeh/GKxlfhlYXSdgU7CRLxm58GC42za3tDuC4NJld/k=.ed25519~iyaCpZ0co863K9aF+b7j8BnnHfwY65dGeX6Dh2nXs3c=| |Lohn's Pub| @lohn |p.lohn.in:8018:@LohnKVll9HdLI3AndEc4zwGtfdF/J7xC7PW9B/JpI4U=.ed25519~z3m4ttJdI4InHkCtchxTu26kKqOfKk4woBb1TtPeA/s=| | Scuttle Space | @guil-dot | Visit scuttle.space | |SSB PeerNet US-East| timjrobinson |us-east.ssbpeer.net:8008:@sTO03jpVivj65BEAJMhlwtHXsWdLd9fLwyKAT1qAkc0=.ed25519~sXFc5taUA7dpGTJITZVDCRy2A9jmkVttsr107+ufInU=| | Hermies | s | net:hermies.club:8008~shs:uMYDVPuEKftL4SzpRGVyQxLdyPkOiX7njit7+qT/7IQ=:SSB+Room+PSK3TLYC2T86EHQCUHBUHASCASE18JBV24= |GUI - Interface Gráfica do Utilizador(Usuário)
Patchwork - Uma GUI SSB (Descontinuado)
Patchwork é o aplicativo de mensagens e compartilhamento descentralizado construído em cima do SSB . O protocolo scuttlebutt em si não mantém um conjunto de feeds nos quais um usuário está interessado, então um cliente é necessário para manter uma lista de feeds de pares em que seu respectivo usuário está interessado e seguindo.

Fonte: scuttlebutt.nz
Quando você instala e executa o Patchwork, você só pode ver e se comunicar com seus pares em sua rede local. Para acessar fora de sua LAN, você precisa se conectar a um Pub. Um pub é apenas para convidados e eles retransmitem mensagens entre você e seus pares fora de sua LAN e entre outros Pubs.
Lembre-se de que você precisa seguir alguém para receber mensagens dessa pessoa. Isso reduz o envio de mensagens de spam para os usuários. Os usuários só veem as respostas das pessoas que seguem. Os dados são sincronizados no disco para funcionar offline, mas podem ser sincronizados diretamente com os pares na sua LAN por wi-fi ou bluetooth.
Patchbay - Uma GUI Alternativa
Patchbay é um cliente de fofoca projetado para ser fácil de modificar e estender. Ele usa o mesmo banco de dados que Patchwork e Patchfoo , então você pode facilmente dar uma volta com sua identidade existente.

Planetary - GUI para IOS

Planetary é um app com pubs pré-carregados para facilitar integração.
Manyverse - GUI para Android

Manyverse é um aplicativo de rede social com recursos que você esperaria: posts, curtidas, perfis, mensagens privadas, etc. Mas não está sendo executado na nuvem de propriedade de uma empresa, em vez disso, as postagens de seus amigos e todos os seus dados sociais vivem inteiramente em seu telefone .
Fontes
-
https://scuttlebot.io/
-
https://decentralized-id.com/decentralized-web/scuttlebot/#plugins
-
https://medium.com/@miguelmota/getting-started-with-secure-scuttlebut-e6b7d4c5ecfd
-
Secure Scuttlebutt : um protocolo de banco de dados global.
-
-
 @ 6be5cc06:5259daf0
2024-12-29 19:54:14
@ 6be5cc06:5259daf0
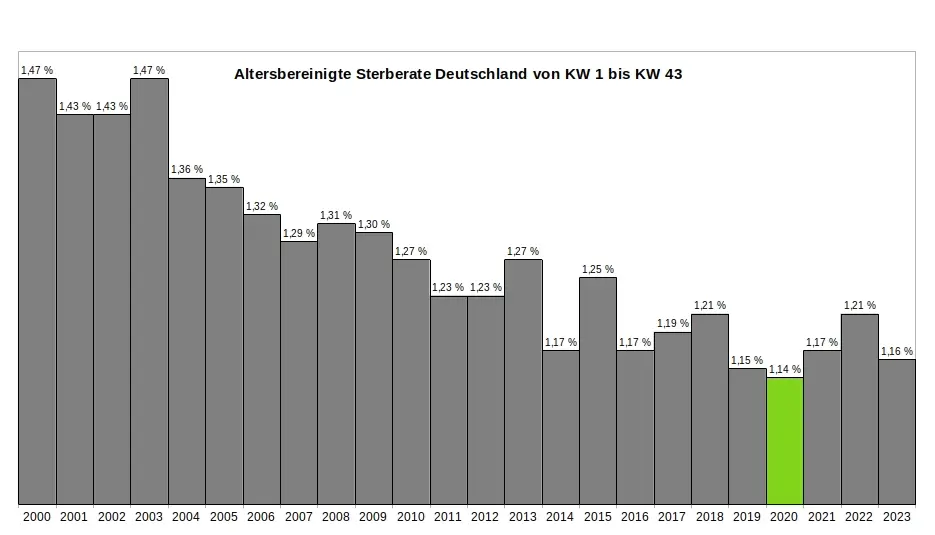
2024-12-29 19:54:14Um dos padrões mais bem estabelecidos ao medir a opinião pública é que cada geração tende a seguir um caminho semelhante em termos de política e ideologia geral. Seus membros compartilham das mesmas experiências formativas, atingem os marcos importantes da vida ao mesmo tempo e convivem nos mesmos espaços. Então, como devemos entender os relatórios que mostram que a Geração Z é hiperprogressista em certos assuntos, mas surpreendentemente conservadora em outros?
A resposta, nas palavras de Alice Evans, pesquisadora visitante na Universidade de Stanford e uma das principais estudiosas do tema, é que os jovens de hoje estão passando por um grande divergência de gênero, com as jovens mulheres do primeiro grupo e os jovens homens do segundo. A Geração Z representa duas gerações, e não apenas uma.
Em países de todos os continentes, surgiu um distanciamento ideológico entre jovens homens e mulheres. Milhões de pessoas que compartilham das mesmas cidades, locais de trabalho, salas de aula e até casas, não veem mais as coisas da mesma maneira.
Nos Estados Unidos, os dados da Gallup mostram que, após décadas em que os sexos estavam distribuídos de forma relativamente equilibrada entre visões políticas liberais e conservadoras, as mulheres entre 18 e 30 anos são agora 30 pontos percentuais mais liberais do que os homens dessa faixa etária. Essa diferença surgiu em apenas seis anos.
A Alemanha também apresenta um distanciamento de 30 pontos entre homens jovens conservadores e mulheres jovens progressistas, e no Reino Unido, a diferença é de 25 pontos. Na Polônia, no ano passado, quase metade dos homens entre 18 e 21 anos apoiou o partido de extrema direita Confederation, em contraste com apenas um sexto das jovens mulheres dessa mesma idade.
Fora do Ocidente, há divisões ainda mais acentuadas. Na Coreia do Sul, há um enorme abismo entre homens e mulheres jovens, e a situação é semelhante na China. Na África, a Tunísia apresenta o mesmo padrão. Vale notar que em todos os países essa divisão drástica ocorre principalmente entre a geração mais jovem, sendo muito menos pronunciada entre homens e mulheres na faixa dos 30 anos ou mais velhos.
O movimento # MeToo foi o principal estopim, trazendo à tona valores feministas intensos entre jovens mulheres que se sentiram empoderadas para denunciar injustiças de longa data. Esse estopim encontrou especialmente terreno fértil na Coreia do Sul, onde a desigualdade de gênero é bastante visível e a misoginia explícita é comum. (palavras da Financial Times, eu só traduzi)
Na eleição presidencial da Coreia do Sul em 2022, enquanto homens e mulheres mais velhos votaram de forma unificada, os jovens homens apoiaram fortemente o partido de direita People Power, enquanto as jovens mulheres apoiaram o partido liberal Democratic em números quase iguais e opostos.
A situação na Coreia é extrema, mas serve como um alerta para outros países sobre o que pode acontecer quando jovens homens e mulheres se distanciam. A sociedade está dividida, a taxa de casamento despencou e a taxa de natalidade caiu drasticamente, chegando a 0,78 filhos por mulher em 2022, o menor número no mundo todo.
Sete anos após a explosão inicial do movimento # MeToo, a divergência de gênero em atitudes tornou-se autossustentável.
Dados das pesquisas mostram que em muitos países, as diferenças ideológicas vão além dessa questão específica. A divisão progressista-conservadora sobre assédio sexual parece ter causado ou pelo menos faz parte de um alinhamento mais amplo, em que jovens homens e mulheres estão se organizando em grupos conservadores e liberais em outros assuntos.
Nos EUA, Reino Unido e Alemanha, as jovens mulheres agora adotam posturas mais liberais sobre temas como imigração e justiça racial, enquanto grupos etários mais velhos permanecem equilibrados. A tendência na maioria dos países tem sido de mulheres se inclinando mais para a esquerda, enquanto os homens permanecem estáveis. No entanto, há sinais de que os jovens homens estão se movendo para a direita na Alemanha, tornando-se mais críticos em relação à imigração e se aproximando do partido de extrema direita AfD nos últimos anos.
Seria fácil dizer que tudo isso é apenas uma fase passageira, mas os abismos ideológicos apenas crescem, e os dados mostram que as experiências políticas formativas das pessoas são difíceis de mudar. Tudo isso é agravado pelo fato de que o aumento dos smartphones e das redes sociais faz com que os jovens homens e mulheres agora vivam em espaços separados e tenham culturas distintas.
As opiniões dos jovens frequentemente são ignoradas devido à baixa participação política, mas essa mudança pode deixar consequências duradouras, impactando muito mais do que apenas os resultados das eleições.
Retirado de: https://www.ft.com/content/29fd9b5c-2f35-41bf-9d4c-994db4e12998
-
 @ 6f3670d9:03f04036
2024-12-29 08:20:22
@ 6f3670d9:03f04036
2024-12-29 08:20:22Disclaimer: - This will void your warranty - There might be differences between the Bitaxe and the Lucky Miner that might not cause issues or damage immediately, but might manifest long-term - Proceed at your own risk
A Different Pickaxe
You live in a place where it's difficult to get a Bitaxe. You have access to AliExpress. You look around. You find something called the "Lucky Miner LV06". A Bitaxe clone that uses the same mining chip as the Bitaxe Ultra (BM1366 ASIC). You buy one.
You plug it in, you enter your wallet address and other settings, and it starts mining. It works! Great!
But it's running a customized firmware. It's not AxeOS. Maybe there's something shady in the stock firmware. It's not open-source, after all. Also, AxeOS looks amazing... And that automatic pool fail-over feature is handy.
You think to yourself: "Maybe I can use the Bitaxe firmware on this?". Guess what? You're right!
Flashing From Web UI
What usually works for me is to: - Download the Bitaxe firmware files (
esp-miner.binandwww.bin) from GitHub (here). Version 2.4.1 seems to work well, as of this writing. - Then from the Lucky Miner web interface, upload the "Website" (www.bin) file. - Wait for a minute or two after it's done uploading. - Upload the "Firmware" (esp-miner.bin) file. - Wait another minute or two. - Unplug the power and plug it back in. - Set the "Core Voltage" and "Frequency" to the defaults. - Unplug the power and plug it back in again.If you're lucky (no pun intended), you'll have a working Lucky Miner with AxeOS. Update the settings and mine away!
However, often times I've been unlucky, like what happened while I was writing this article, ironically. The miner malfunctions for no obvious reason. It keeps rebooting, or it's not mining (zero/low hashrate), or the web interface is inaccessible. You name it.
The miner has become a "brick". How do you "unbrick" it?
When you brick a Bitaxe, you can recover it by flashing (uploading) a "Factory Image". The Bitaxe has a USB port that makes this easy. Follow the guide and it should come back to life again. Unfortunately, the Lucky Miner LV06 doesn't have a USB port. It has a serial port, though. We'll have to get our hands a bit dirty.
Flashing Using the Serial Port
We need to connect the serial port of the miner to a computer and run a program to flash (upload) the firmware file on the miner. Any 3.3v UART serial port should be sufficient. Unfortunately, PCs don't usually come with a UART serial port these days, let alone a 3.3v one. The serial port common in old computers is an RS-232 port, which will most probably fry your miner if you try to connect it directly. Beware.
In my case, as a serial port for my PC, I'm using an Arduino Due I had lying around. We connect it to the PC through USB, and on the other side we connect a few wires to the miner, which gives the PC access to the miner.
WARNING: Make sure your serial port is 3.3v or you will probably kill the miner. Arduino Uno is 5v not 3.3v, for example, and cannot be used for this.
Wiring
First, we need to open the Lucky Miner. Use a small flat screwdriver to gently push the two plastic clips shown in the picture below. Gently pry the top cover away from the bottom cover on the clips side first, then remove the other side. Be careful not to break the display cable.
Once the cover is off, you can find the miner's serial port in the top right corner (J10), as shown in the next picture. We'll also need the reset button (EN).
There are three screws holding the PCB and the bottom cover together. If you're confident in your ability to push the small button on the underside of the PCB with the bottom cover on, then no need to remove these. The following picture shows what we need from that side.
And the next picture shows the pins and USB port we will use from the Arduino.
Now, we need to connect: - The USB port on the Arduino labelled "programming" to the PC - Pin 18 (TX1) on the Arduino to J10 through-hole pad 5 (blue dot) - Pin 19 (RX1) on the Arduino to J10 through-hole pad 3 (green dot) - Any GND pin on the Arduino to J10 through-hole pad 4 (yellow dot)
I didn't need to solder the wires to the pads. Keeping everything stable, perhaps by putting a weight on the wires or a bit of tape, was sufficient in all my attempts.
Setting up the Arduino
To use the Arduino as a serial port for our PC, we'll have to make it pass-through data back and forth between the USB port and UART1, where we connected the miner.
The following steps are all done on a PC running Debian Linux (Bookworm), in the spirit of freedom and open-source.
First, we start the Arduino IDE. If the package for the Arduino Due board is not already installed, you'll see a small prompt at the bottom. Click "Install this package".
Click the "Install" button.
Once the package is installed, click "Close".
Next, we select the Due board. Click the "Tools" menu, select "Board", select "Arduino ARM (32-bits) Boards" and click "Arduino Due (Programming Port)"
Next, we select the port. Click the "Tools" menu again, select "Port", and click the port where the Arduino is connected. In my case it was "/dev/ttyACM0".
Now we need to upload the following code to the Arduino board. The code is actually the "SerialPassthrough" example from the IDE, but with the serial speed changed to match the miner.
``` void setup() { Serial.begin(115200); Serial1.begin(115200); }
void loop() { if (Serial.available()) { // If anything comes in Serial (USB), Serial1.write(Serial.read()); // read it and send it out Serial1 }
if (Serial1.available()) { // If anything comes in Serial1 Serial.write(Serial1.read()); // read it and send it out Serial (USB) } } ```
Copy/paste the code into the IDE and click upload. You'll see "Done uploading" at the bottom.
Next we'll test if we're receiving data from the miner. We start by opening the "Serial Monitor" from the "Tools" menu in the IDE. Then we change the baudrate to 115200.
Set the Arduino and the miner in a comfortable position, make sure the wires are held in place and got a good contact on both sides, and the power is plugged in.
Now we'll put the miner in "download" mode. Press and hold the button on the underside (K1), press and release the reset button (EN), then release the other button (K1).
You should see some text from the miner in the serial monitor window, like in the picture below.
Congratulations! We know we're able to receive data from the miner now. We're not sure transmit is working, but we'll find out when we try to flash.
Flashing Using the Serial Port, for Real
To flash the Lucky Miner we'll need a software tool named esptool and the factory image firmware file.
I usually use "esp-miner-factory-205-v2.1.8.bin" for the factory image (this one) as a base, and then flash the version I want from the Web UI, using the steps I mentioned earlier.
For esptool, the documentation (here) shows us how to install it. To make things a little easier on our Debian Linux system, we'll use pipx instead of pip. The instructions below are adapted for that.
First we make sure pipx is installed. Run this command in a terminal and follow the instructions:
sudo apt-get install pipxThen we install esptool using pipx. Run the following in a terminal:
pipx install esptoolThe output will be something like this:
user@pc:~$ pipx install esptool installed package esptool 4.8.1, installed using Python 3.11.2 These apps are now globally available - esp_rfc2217_server.py - espefuse.py - espsecure.py - esptool.py ⚠️ Note: '/home/user/.local/bin' is not on your PATH environment variable. These apps will not be globally accessible until your PATH is updated. Run `pipx ensurepath` to automatically add it, or manually modify your PATH in your shell's config file (i.e. ~/.bashrc). done! ✨ 🌟 ✨We can see pipx telling us we won't be able to run our tool because the folder where it was installed is not in the PATH variable. To fix that, we can follow pipx instructions and run:
pipx ensurepathAnd we'll see something like this:
``` user@pc:~$ pipx ensurepath Success! Added /home/user/.local/bin to the PATH environment variable.
Consider adding shell completions for pipx. Run 'pipx completions' for instructions.
You will need to open a new terminal or re-login for the PATH changes to take effect.
Otherwise pipx is ready to go! ✨ 🌟 ✨ ```
Now, close the terminal and re-open it so that esptool becomes available.
Finally, to actually flash the miner, put the miner in download mode, then in the following command change the port ("/dev/ttyACM0") to your serial port, as we've seen earlier, and the file path to where your firmware file is, and run it:
esptool.py -p /dev/ttyACM0 --baud 115200 write_flash --erase-all 0x0 ~/Downloads/esp-miner-factory-205-v2.1.8.binIf everything went fine, the tool will take a few minutes to flash the firmware to the miner. You'll see something like this in the output:
``` user@pc:~$ esptool.py -p /dev/ttyACM0 --baud 115200 write_flash --erase-all 0x0 ~/Downloads/esp-miner-factory-205-v2.1.8.bin esptool.py v4.8.1 Serial port /dev/ttyACM0 Connecting..... Detecting chip type... ESP32-S3 Chip is ESP32-S3 (QFN56) (revision v0.2) Features: WiFi, BLE, Embedded PSRAM 8MB (AP_3v3) Crystal is 40MHz MAC: 3c:84:27:ba:be:01 Uploading stub... Running stub... Stub running... Configuring flash size... Erasing flash (this may take a while)... Chip erase completed successfully in 9.5s Compressed 15802368 bytes to 1320190... Wrote 15802368 bytes (1320190 compressed) at 0x00000000 in 152.1 seconds (effective 831.2 kbit/s)... Hash of data verified.
Leaving... Hard resetting via RTS pin... ```
And we're done! Hopefully the miner will be recovered now.
Hope this helps!
Stay humble,
dumb-packageA Warning About Beta Versions of AxeOS
For reasons unknown to me, while I was writing this article I wanted to try the testing version of AxeOS, which was v2.4.1b (beta). Flashing from Web UI went smooth, but the miner stopped mining. I flashed back to v2.1.8 using the serial port, a known good version for me, but it wouldn't mine, still.
Thankfully, v2.4.1 was released recently, and flashing it from the Web UI magically revived my miner. So, be warned.
Bonus: File Hashes
For convenience, these are the SHA256 hashes of the files I used in this article: ``` da24fceb246f3b8b4dd94e5143f17bd38e46e5285e807ebd51627cb08f665c0a ESP-Miner-v2.4.1/esp-miner.bin 16c5c671391f0e3e88a3e79ce33fad3b0ec232b8572fad5e1e0d1ad3251ab394 ESP-Miner-v2.4.1/www.bin
d5182a15b6fa21d7b9b31bff2026d30afed9d769781a48db914730a5751e20c6 esp-miner-factory-205-v2.1.8.bin ```
-
 @ 6f3670d9:03f04036
2024-12-29 06:51:25
@ 6f3670d9:03f04036
2024-12-29 06:51:25This is my first long-form post. The starting line.
There's nothing of value here. Just using this as a marker.
I hope to post a lot more. Documenting how I made something work would be very useful to me, and hopefully others, but I've been too lazy to do that. Wish me luck!
Stay humble,
dumb-package -
 @ 9f94e6cc:f3472946
2024-11-21 18:55:12
@ 9f94e6cc:f3472946
2024-11-21 18:55:12Der Entartungswettbewerb TikTok hat die Jugend im Griff und verbrutzelt ihre Hirne. Über Reels, den Siegeszug des Hochformats und die Regeln der Viralität.
Text: Aron Morhoff
Hollywood steckt heute in der Hosentasche. 70 Prozent aller YouTube-Inhalte werden auf mobilen Endgeräten, also Smartphones, geschaut. Instagram und TikTok sind die angesagtesten Anwendungen für junge Menschen. Es gibt sie nur noch als App, und ihr Design ist für Mobiltelefone optimiert.
Einst waren Rechner und Laptops die Tools, mit denen ins Internet gegangen wurde. Auch als das Smartphone seinen Siegeszug antrat, waren die Sehgewohnheiten noch auf das Querformat ausgerichtet. Heute werden Rechner fast nur noch zum Arbeiten verwendet. Das Berieseln, die Unterhaltung, das passive Konsumieren hat sich vollständig auf die iPhones und Samsungs dieser Welt verlagert. Das Telefon hat den aufrechten Gang angenommen, kaum einer mehr hält sein Gerät waagerecht.
Homo Digitalis Erectus
Die Welt steht also Kopf. Die Form eines Mediums hat Einfluss auf den Inhalt. Marshall McLuhan formulierte das so: Das Medium selbst ist die Botschaft. Ja mei, mag sich mancher denken, doch medienanthropologisch ist diese Entwicklung durchaus eine Betrachtung wert. Ein Querformat eignet sich besser, um Landschaften, einen Raum oder eine Gruppe abzubilden. Das Hochformat entspricht grob den menschlichen Maßen von der Hüfte bis zum Kopf. Der TikTok-Tanz ist im Smartphone-Design also schon angelegt. Das Hochformat hat die Medieninhalte unserer Zeit noch narzisstischer gemacht.
Dass wir uns durch Smartphones freizügiger und enthemmter zur Schau stellen, ist bekannt. 2013 wurde „Selfie“ vom Oxford English Dictionary zum Wort des Jahres erklärt. Selfie, Selbstporträt, Selbstdarstellung.
Neu ist der Aufwand, der heute vonnöten ist, um die Aufmerksamkeitsschwelle der todamüsierten Mediengesellschaft überhaupt noch zu durchbrechen. In beängstigender Hypnose erwischt man viele Zeitgenossen inzwischen beim Doomscrollen. Das ist der Fachbegriff für das weggetretene Endloswischen und erklärt auch den Namen „Reel“: Der Begriff, im Deutschen verwandt mit „Rolle“, beschreibt die Filmrolle, von der 24 Bilder pro Sekunde auf den Projektor gewischt oder eben abgespult werden.
Länger als drei Sekunden darf ein Kurzvideo deshalb nicht mehr gehen, ohne dass etwas Aufregendes passiert. Sonst wird das Reel aus Langeweile weggewischt. Die Welt im Dopamin-Rausch. Für den Ersteller eines Videos heißt das inzwischen: Sei der lauteste, schrillste, gestörteste Marktschreier. Das Wettrennen um die Augäpfel zwingt zu extremen Formen von Clickbait.
15 Sekunden Ruhm
Das nimmt inzwischen skurrile Formen an. Das Video „Look who I found“ von Noel Robinson (geboren 2001) war im letzten Jahr einer der erfolgreichsten deutschen TikTok-Clips. Man sieht den Deutsch-Nigerianer beim Antanzen eines karikaturartig übergewichtigen Menschen. Noel wird geschubst und fällt. Daraufhin wechselt das Lied – und der fette Mann bewegt seinen Schwabbelbauch im Takt. Noel steht wieder auf, grinst, beide tanzen gemeinsam. Das dauert 15 Sekunden. Ich rate Ihnen, sich das Video einmal anzuschauen, um die Mechanismen von TikTok zu verstehen. Achten Sie alleine darauf, wie vielen Reizen (Menschenmenge, Antanzen, Sturz, Schwabbelbauch) Sie in den ersten fünf Sekunden ausgesetzt sind. Wer schaut so was? Bis dato 220 Millionen Menschen. Das ist kapitalistische Verwertungslogik im bereits verwesten Endstadium. Adorno oder Fromm hätten am Medienzeitgeist entweder ihre Freude oder mächtig zu knabbern.
Die Internet- und Smartphoneabdeckung beträgt mittlerweile fast 100 Prozent. Das Überangebot hat die Regeln geändert. Um überhaupt gesehen zu werden, muss man heute viral gehen. Was dafür inzwischen nötig ist, spricht die niedrigsten Bedürfnisse des Menschen an: Gewalt, Ekel, Sexualisierung, Schock. Die jungen Erwachsenen, die heute auf sozialen Netzwerken den Ton angeben, haben diese Mechanismen längst verinnerlicht. Wie bewusst ihnen das ist, ist fraglich. 2024 prallt eine desaströse Bildungssituation samt fehlender Medienkompetenz auf eine egomanische Jugend, die Privatsphäre nie gekannt hat und seit Kindesbeinen alles in den Äther ballert, was es festhalten kann. Man muss kein Kulturpessimist sein, um diese degenerative Dynamik, auch in ihrer Implikation für unser Zusammenleben und das psychische Wohlergehen der Generation TikTok, als beängstigend zu bezeichnen.
Aron Morhoff studierte Medienethik und ist Absolvent der Freien Akademie für Medien & Journalismus. Frühere Stationen: RT Deutsch und Nuoviso. Heute: Stichpunkt Magazin, Manova, Milosz Matuschek und seine Liveshow "Addictive Programming".
-
 @ eac63075:b4988b48
2024-11-09 17:57:27
@ eac63075:b4988b48
2024-11-09 17:57:27Based on a recent paper that included collaboration from renowned experts such as Lynn Alden, Steve Lee, and Ren Crypto Fish, we discuss in depth how Bitcoin's consensus is built, the main risks, and the complex dynamics of protocol upgrades.
Podcast https://www.fountain.fm/episode/wbjD6ntQuvX5u2G5BccC
Presentation https://gamma.app/docs/Analyzing-Bitcoin-Consensus-Risks-in-Protocol-Upgrades-p66axxjwaa37ksn
1. Introduction to Consensus in Bitcoin
Consensus in Bitcoin is the foundation that keeps the network secure and functional, allowing users worldwide to perform transactions in a decentralized manner without the need for intermediaries. Since its launch in 2009, Bitcoin is often described as an "immutable" system designed to resist changes, and it is precisely this resistance that ensures its security and stability.
The central idea behind consensus in Bitcoin is to create a set of acceptance rules for blocks and transactions, ensuring that all network participants agree on the transaction history. This prevents "double-spending," where the same bitcoin could be used in two simultaneous transactions, something that would compromise trust in the network.
Evolution of Consensus in Bitcoin
Over the years, consensus in Bitcoin has undergone several adaptations, and the way participants agree on changes remains a delicate process. Unlike traditional systems, where changes can be imposed from the top down, Bitcoin operates in a decentralized model where any significant change needs the support of various groups of stakeholders, including miners, developers, users, and large node operators.
Moreover, the update process is extremely cautious, as hasty changes can compromise the network's security. As a result, the philosophy of "don't fix what isn't broken" prevails, with improvements happening incrementally and only after broad consensus among those involved. This model can make progress seem slow but ensures that Bitcoin remains faithful to the principles of security and decentralization.
2. Technical Components of Consensus
Bitcoin's consensus is supported by a set of technical rules that determine what is considered a valid transaction and a valid block on the network. These technical aspects ensure that all nodes—the computers that participate in the Bitcoin network—agree on the current state of the blockchain. Below are the main technical components that form the basis of the consensus.
Validation of Blocks and Transactions
The validation of blocks and transactions is the central point of consensus in Bitcoin. A block is only considered valid if it meets certain criteria, such as maximum size, transaction structure, and the solving of the "Proof of Work" problem. The proof of work, required for a block to be included in the blockchain, is a computational process that ensures the block contains significant computational effort—protecting the network against manipulation attempts.
Transactions, in turn, need to follow specific input and output rules. Each transaction includes cryptographic signatures that prove the ownership of the bitcoins sent, as well as validation scripts that verify if the transaction conditions are met. This validation system is essential for network nodes to autonomously confirm that each transaction follows the rules.
Chain Selection
Another fundamental technical issue for Bitcoin's consensus is chain selection, which becomes especially important in cases where multiple versions of the blockchain coexist, such as after a network split (fork). To decide which chain is the "true" one and should be followed, the network adopts the criterion of the highest accumulated proof of work. In other words, the chain with the highest number of valid blocks, built with the greatest computational effort, is chosen by the network as the official one.
This criterion avoids permanent splits because it encourages all nodes to follow the same main chain, reinforcing consensus.
Soft Forks vs. Hard Forks
In the consensus process, protocol changes can happen in two ways: through soft forks or hard forks. These variations affect not only the protocol update but also the implications for network users:
-
Soft Forks: These are changes that are backward compatible. Only nodes that adopt the new update will follow the new rules, but old nodes will still recognize the blocks produced with these rules as valid. This compatibility makes soft forks a safer option for updates, as it minimizes the risk of network division.
-
Hard Forks: These are updates that are not backward compatible, requiring all nodes to update to the new version or risk being separated from the main chain. Hard forks can result in the creation of a new coin, as occurred with the split between Bitcoin and Bitcoin Cash in 2017. While hard forks allow for deeper changes, they also bring significant risks of network fragmentation.
These technical components form the base of Bitcoin's security and resilience, allowing the system to remain functional and immutable without losing the necessary flexibility to evolve over time.
3. Stakeholders in Bitcoin's Consensus
Consensus in Bitcoin is not decided centrally. On the contrary, it depends on the interaction between different groups of stakeholders, each with their motivations, interests, and levels of influence. These groups play fundamental roles in how changes are implemented or rejected on the network. Below, we explore the six main stakeholders in Bitcoin's consensus.
1. Economic Nodes
Economic nodes, usually operated by exchanges, custody providers, and large companies that accept Bitcoin, exert significant influence over consensus. Because they handle large volumes of transactions and act as a connection point between the Bitcoin ecosystem and the traditional financial system, these nodes have the power to validate or reject blocks and to define which version of the software to follow in case of a fork.
Their influence is proportional to the volume of transactions they handle, and they can directly affect which chain will be seen as the main one. Their incentive is to maintain the network's stability and security to preserve its functionality and meet regulatory requirements.
2. Investors
Investors, including large institutional funds and individual Bitcoin holders, influence consensus indirectly through their impact on the asset's price. Their buying and selling actions can affect Bitcoin's value, which in turn influences the motivation of miners and other stakeholders to continue investing in the network's security and development.
Some institutional investors have agreements with custodians that may limit their ability to act in network split situations. Thus, the impact of each investor on consensus can vary based on their ownership structure and how quickly they can react to a network change.
3. Media Influencers
Media influencers, including journalists, analysts, and popular personalities on social media, have a powerful role in shaping public opinion about Bitcoin and possible updates. These influencers can help educate the public, promote debates, and bring transparency to the consensus process.
On the other hand, the impact of influencers can be double-edged: while they can clarify complex topics, they can also distort perceptions by amplifying or minimizing change proposals. This makes them a force both of support and resistance to consensus.
4. Miners
Miners are responsible for validating transactions and including blocks in the blockchain. Through computational power (hashrate), they also exert significant influence over consensus decisions. In update processes, miners often signal their support for a proposal, indicating that the new version is safe to use. However, this signaling is not always definitive, and miners can change their position if they deem it necessary.
Their incentive is to maximize returns from block rewards and transaction fees, as well as to maintain the value of investments in their specialized equipment, which are only profitable if the network remains stable.
5. Protocol Developers
Protocol developers, often called "Core Developers," are responsible for writing and maintaining Bitcoin's code. Although they do not have direct power over consensus, they possess an informal veto power since they decide which changes are included in the main client (Bitcoin Core). This group also serves as an important source of technical knowledge, helping guide decisions and inform other stakeholders.
Their incentive lies in the continuous improvement of the network, ensuring security and decentralization. Many developers are funded by grants and sponsorships, but their motivations generally include a strong ideological commitment to Bitcoin's principles.
6. Users and Application Developers
This group includes people who use Bitcoin in their daily transactions and developers who build solutions based on the network, such as wallets, exchanges, and payment platforms. Although their power in consensus is less than that of miners or economic nodes, they play an important role because they are responsible for popularizing Bitcoin's use and expanding the ecosystem.
If application developers decide not to adopt an update, this can affect compatibility and widespread acceptance. Thus, they indirectly influence consensus by deciding which version of the protocol to follow in their applications.
These stakeholders are vital to the consensus process, and each group exerts influence according to their involvement, incentives, and ability to act in situations of change. Understanding the role of each makes it clearer how consensus is formed and why it is so difficult to make significant changes to Bitcoin.
4. Mechanisms for Activating Updates in Bitcoin
For Bitcoin to evolve without compromising security and consensus, different mechanisms for activating updates have been developed over the years. These mechanisms help coordinate changes among network nodes to minimize the risk of fragmentation and ensure that updates are implemented in an orderly manner. Here, we explore some of the main methods used in Bitcoin, their advantages and disadvantages, as well as historical examples of significant updates.
Flag Day
The Flag Day mechanism is one of the simplest forms of activating changes. In it, a specific date or block is determined as the activation moment, and all nodes must be updated by that point. This method does not involve prior signaling; participants simply need to update to the new software version by the established day or block.
-
Advantages: Simplicity and predictability are the main benefits of Flag Day, as everyone knows the exact activation date.
-
Disadvantages: Inflexibility can be a problem because there is no way to adjust the schedule if a significant part of the network has not updated. This can result in network splits if a significant number of nodes are not ready for the update.
An example of Flag Day was the Pay to Script Hash (P2SH) update in 2012, which required all nodes to adopt the change to avoid compatibility issues.
BIP34 and BIP9
BIP34 introduced a more dynamic process, in which miners increase the version number in block headers to signal the update. When a predetermined percentage of the last blocks is mined with this new version, the update is automatically activated. This model later evolved with BIP9, which allowed multiple updates to be signaled simultaneously through "version bits," each corresponding to a specific change.
-
Advantages: Allows the network to activate updates gradually, giving more time for participants to adapt.
-
Disadvantages: These methods rely heavily on miner support, which means that if a sufficient number of miners do not signal the update, it can be delayed or not implemented.
BIP9 was used in the activation of SegWit (BIP141) but faced challenges because some miners did not signal their intent to activate, leading to the development of new mechanisms.
User Activated Soft Forks (UASF) and User Resisted Soft Forks (URSF)
To increase the decision-making power of ordinary users, the concept of User Activated Soft Fork (UASF) was introduced, allowing node operators, not just miners, to determine consensus for a change. In this model, nodes set a date to start rejecting blocks that are not in compliance with the new update, forcing miners to adapt or risk having their blocks rejected by the network.
URSF, in turn, is a model where nodes reject blocks that attempt to adopt a specific update, functioning as resistance against proposed changes.
-
Advantages: UASF returns decision-making power to node operators, ensuring that changes do not depend solely on miners.
-
Disadvantages: Both UASF and URSF can generate network splits, especially in cases of strong opposition among different stakeholders.
An example of UASF was the activation of SegWit in 2017, where users supported activation independently of miner signaling, which ended up forcing its adoption.
BIP8 (LOT=True)
BIP8 is an evolution of BIP9, designed to prevent miners from indefinitely blocking a change desired by the majority of users and developers. BIP8 allows setting a parameter called "lockinontimeout" (LOT) as true, which means that if the update has not been fully signaled by a certain point, it is automatically activated.
-
Advantages: Ensures that changes with broad support among users are not blocked by miners who wish to maintain the status quo.
-
Disadvantages: Can lead to network splits if miners or other important stakeholders do not support the update.
Although BIP8 with LOT=True has not yet been used in Bitcoin, it is a proposal that can be applied in future updates if necessary.
These activation mechanisms have been essential for Bitcoin's development, allowing updates that keep the network secure and functional. Each method brings its own advantages and challenges, but all share the goal of preserving consensus and network cohesion.
5. Risks and Considerations in Consensus Updates
Consensus updates in Bitcoin are complex processes that involve not only technical aspects but also political, economic, and social considerations. Due to the network's decentralized nature, each change brings with it a set of risks that need to be carefully assessed. Below, we explore some of the main challenges and future scenarios, as well as the possible impacts on stakeholders.
Network Fragility with Alternative Implementations
One of the main risks associated with consensus updates is the possibility of network fragmentation when there are alternative software implementations. If an update is implemented by a significant group of nodes but rejected by others, a network split (fork) can occur. This creates two competing chains, each with a different version of the transaction history, leading to unpredictable consequences for users and investors.
Such fragmentation weakens Bitcoin because, by dividing hashing power (computing) and coin value, it reduces network security and investor confidence. A notable example of this risk was the fork that gave rise to Bitcoin Cash in 2017 when disagreements over block size resulted in a new chain and a new asset.
Chain Splits and Impact on Stakeholders
Chain splits are a significant risk in update processes, especially in hard forks. During a hard fork, the network is split into two separate chains, each with its own set of rules. This results in the creation of a new coin and leaves users with duplicated assets on both chains. While this may seem advantageous, in the long run, these splits weaken the network and create uncertainties for investors.
Each group of stakeholders reacts differently to a chain split:
-
Institutional Investors and ETFs: Face regulatory and compliance challenges because many of these assets are managed under strict regulations. The creation of a new coin requires decisions to be made quickly to avoid potential losses, which may be hampered by regulatory constraints.
-
Miners: May be incentivized to shift their computing power to the chain that offers higher profitability, which can weaken one of the networks.
-
Economic Nodes: Such as major exchanges and custody providers, have to quickly choose which chain to support, influencing the perceived value of each network.
Such divisions can generate uncertainties and loss of value, especially for institutional investors and those who use Bitcoin as a store of value.
Regulatory Impacts and Institutional Investors
With the growing presence of institutional investors in Bitcoin, consensus changes face new compliance challenges. Bitcoin ETFs, for example, are required to follow strict rules about which assets they can include and how chain split events should be handled. The creation of a new asset or migration to a new chain can complicate these processes, creating pressure for large financial players to quickly choose a chain, affecting the stability of consensus.
Moreover, decisions regarding forks can influence the Bitcoin futures and derivatives market, affecting perception and adoption by new investors. Therefore, the need to avoid splits and maintain cohesion is crucial to attract and preserve the confidence of these investors.
Security Considerations in Soft Forks and Hard Forks
While soft forks are generally preferred in Bitcoin for their backward compatibility, they are not without risks. Soft forks can create different classes of nodes on the network (updated and non-updated), which increases operational complexity and can ultimately weaken consensus cohesion. In a network scenario with fragmentation of node classes, Bitcoin's security can be affected, as some nodes may lose part of the visibility over updated transactions or rules.
In hard forks, the security risk is even more evident because all nodes need to adopt the new update to avoid network division. Experience shows that abrupt changes can create temporary vulnerabilities, in which malicious agents try to exploit the transition to attack the network.
Bounty Claim Risks and Attack Scenarios
Another risk in consensus updates are so-called "bounty claims"—accumulated rewards that can be obtained if an attacker manages to split or deceive a part of the network. In a conflict scenario, a group of miners or nodes could be incentivized to support a new update or create an alternative version of the software to benefit from these rewards.
These risks require stakeholders to carefully assess each update and the potential vulnerabilities it may introduce. The possibility of "bounty claims" adds a layer of complexity to consensus because each interest group may see a financial opportunity in a change that, in the long term, may harm network stability.
The risks discussed above show the complexity of consensus in Bitcoin and the importance of approaching it gradually and deliberately. Updates need to consider not only technical aspects but also economic and social implications, in order to preserve Bitcoin's integrity and maintain trust among stakeholders.
6. Recommendations for the Consensus Process in Bitcoin
To ensure that protocol changes in Bitcoin are implemented safely and with broad support, it is essential that all stakeholders adopt a careful and coordinated approach. Here are strategic recommendations for evaluating, supporting, or rejecting consensus updates, considering the risks and challenges discussed earlier, along with best practices for successful implementation.
1. Careful Evaluation of Proposal Maturity
Stakeholders should rigorously assess the maturity level of a proposal before supporting its implementation. Updates that are still experimental or lack a robust technical foundation can expose the network to unnecessary risks. Ideally, change proposals should go through an extensive testing phase, have security audits, and receive review and feedback from various developers and experts.
2. Extensive Testing in Secure and Compatible Networks
Before an update is activated on the mainnet, it is essential to test it on networks like testnet and signet, and whenever possible, on other compatible networks that offer a safe and controlled environment to identify potential issues. Testing on networks like Litecoin was fundamental for the safe launch of innovations like SegWit and the Lightning Network, allowing functionalities to be validated on a lower-impact network before being implemented on Bitcoin.
The Liquid Network, developed by Blockstream, also plays an important role as an experimental network for new proposals, such as OP_CAT. By adopting these testing environments, stakeholders can mitigate risks and ensure that the update is reliable and secure before being adopted by the main network.
3. Importance of Stakeholder Engagement
The success of a consensus update strongly depends on the active participation of all stakeholders. This includes economic nodes, miners, protocol developers, investors, and end users. Lack of participation can lead to inadequate decisions or even future network splits, which would compromise Bitcoin's security and stability.
4. Key Questions for Evaluating Consensus Proposals
To assist in decision-making, each group of stakeholders should consider some key questions before supporting a consensus change:
- Does the proposal offer tangible benefits for Bitcoin's security, scalability, or usability?
- Does it maintain backward compatibility or introduce the risk of network split?
- Are the implementation requirements clear and feasible for each group involved?
- Are there clear and aligned incentives for all stakeholder groups to accept the change?
5. Coordination and Timing in Implementations
Timing is crucial. Updates with short activation windows can force a split because not all nodes and miners can update simultaneously. Changes should be planned with ample deadlines to allow all stakeholders to adjust their systems, avoiding surprises that could lead to fragmentation.
Mechanisms like soft forks are generally preferable to hard forks because they allow a smoother transition. Opting for backward-compatible updates when possible facilitates the process and ensures that nodes and miners can adapt without pressure.
6. Continuous Monitoring and Re-evaluation
After an update, it's essential to monitor the network to identify problems or side effects. This continuous process helps ensure cohesion and trust among all participants, keeping Bitcoin as a secure and robust network.
These recommendations, including the use of secure networks for extensive testing, promote a collaborative and secure environment for Bitcoin's consensus process. By adopting a deliberate and strategic approach, stakeholders can preserve Bitcoin's value as a decentralized and censorship-resistant network.
7. Conclusion
Consensus in Bitcoin is more than a set of rules; it's the foundation that sustains the network as a decentralized, secure, and reliable system. Unlike centralized systems, where decisions can be made quickly, Bitcoin requires a much more deliberate and cooperative approach, where the interests of miners, economic nodes, developers, investors, and users must be considered and harmonized. This governance model may seem slow, but it is fundamental to preserving the resilience and trust that make Bitcoin a global store of value and censorship-resistant.
Consensus updates in Bitcoin must balance the need for innovation with the preservation of the network's core principles. The development process of a proposal needs to be detailed and rigorous, going through several testing stages, such as in testnet, signet, and compatible networks like Litecoin and Liquid Network. These networks offer safe environments for proposals to be analyzed and improved before being launched on the main network.
Each proposed change must be carefully evaluated regarding its maturity, impact, backward compatibility, and support among stakeholders. The recommended key questions and appropriate timing are critical to ensure that an update is adopted without compromising network cohesion. It's also essential that the implementation process is continuously monitored and re-evaluated, allowing adjustments as necessary and minimizing the risk of instability.
By following these guidelines, Bitcoin's stakeholders can ensure that the network continues to evolve safely and robustly, maintaining user trust and further solidifying its role as one of the most resilient and innovative digital assets in the world. Ultimately, consensus in Bitcoin is not just a technical issue but a reflection of its community and the values it represents: security, decentralization, and resilience.
8. Links
Whitepaper: https://github.com/bitcoin-cap/bcap
Youtube (pt-br): https://www.youtube.com/watch?v=rARycAibl9o&list=PL-qnhF0qlSPkfhorqsREuIu4UTbF0h4zb
-
-
 @ c8841c9d:ae8048e2
2025-02-09 04:37:57
@ c8841c9d:ae8048e2
2025-02-09 04:37:57What is a cryptocurrency ?
Blockchain #Cryptocurrency #Cryptomindmap
A cryptocurrency is a digital currency secured by cryptography.
Cryptocurrency operates on a blockchain network as a distributed ledger, secured by cryptography.
Users own the private and public keys.
For the first time in the digital age, the double spending issue is resolved thanks to the blockchain consensus mechanism. This ensures decentralization and security, creating a trustless environment where transactions are immutable once confirmed.
Cryptocurrency can be categorized in different groups
Bitcoin is the first ever created cryptocurrency on the bitcoin blockchain.
Altcoins is a generic term regrouping every crypto except Bitcoin. There are over a million of ever created Altcoins and more than 20,000 currently active. They can be:
- Coin from a programable blockchain such as Ethereum (ETH), Solana (SOL), Cardano (ADA), or Sui (SUI) for example. Ecosystem of applications are built on top of these blockchain networks.
- Token of Decentralized Application (DApp) built on programmable blockchain such as ChainLink (LINK) or Aave (AAVE) on Ethereum.
- Memecoins are a type of cryptocurrency, typically inspired by internet memes or popular culture, with little or no intrinsic value but cultural and community support. Memecoins such as Dogecoin (DOGE) or Shiba (SHIB) are some of the strongest community in crypto. The price of memecoins is also the most volatile of the entire crypto ecosystem.
A coin is the native cryptocurrency of a blockchain, used for validator rewards and transaction fees. A token, on the other hand, is built on top of an existing blockchain for specific applications.
They are two mains ways to use with cryptocurrencies.
With a wallets for direct blockchain interactions, which contains the keys to necessary for true ownership of the cryptocurrencies, similar to owning cash or any other tangible form of money.
On a centralized exchanges which act as on/off ramps for buying, selling, and keeping crypto. The exchange is in the charge of the private key. It is the equivalent of having money on a bank account.
Remember the saying "Not Your Keys, Not Your Crypto". If you don't control your private keys, you don't truly own your crypto.\ \ Users initiate transactions, send, receive and hold cryptocurrency and their wallet.
Validators ensure blockchain integrity by verifying transactions and building blocks, earning crypto in return.
Developers work on the network infrastructure and the ecosystem, including DApps. While general programming languages can be used, languages specifically designed for blockchain development, like Solidity for Ethereum, have emerged to facilitate crypto development..
Thanks for reading! 🌟 Share in comments your thoughts on cryptocurrency and what topic you would like to be mapped next! #Crypto
-
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ dc4cd086:cee77c06
2025-02-09 03:35:25
@ dc4cd086:cee77c06
2025-02-09 03:35:25Have you ever wanted to learn from lengthy educational videos but found it challenging to navigate through hours of content? Our new tool addresses this problem by transforming long-form video lectures into easily digestible, searchable content.
Key Features:
Video Processing:
- Automatically downloads YouTube videos, transcripts, and chapter information
- Splits transcripts into sections based on video chapters
Content Summarization:
- Utilizes language models to transform spoken content into clear, readable text
- Formats output in AsciiDoc for improved readability and navigation
- Highlights key terms and concepts with [[term]] notation for potential cross-referencing
Diagram Extraction:
- Analyzes video entropy to identify static diagram/slide sections
- Provides a user-friendly GUI for manual selection of relevant time ranges
- Allows users to pick representative frames from selected ranges
Going Forward:
Currently undergoing a rewrite to improve organization and functionality, but you are welcome to try the current version, though it might not work on every machine. Will support multiple open and closed language models for user choice Free and open-source, allowing for personal customization and integration with various knowledge bases. Just because we might not have it on our official Alexandria knowledge base, you are still welcome to use it on you own personal or community knowledge bases! We want to help find connections between ideas that exist across relays, allowing individuals and groups to mix and match knowledge bases between each other, allowing for any degree of openness you care.
While designed with #Alexandria users in mind, it's available for anyone to use and adapt to their own learning needs.
Screenshots
Frame Selection

This is a screenshot of the frame selection interface. You'll see a signal that represents frame entropy over time. The vertical lines indicate the start and end of a chapter. Within these chapters you can select the frames by clicking and dragging the mouse over the desired range where you think diagram is in that chapter. At the bottom is an option that tells the program to select a specific number of frames from that selection.
Diagram Extraction

This is a screenshot of the diagram extraction interface. For every selection you've made, there will be a set of frames that you can choose from. You can select and deselect as many frames as you'd like to save.
Links
- repo: https://github.com/limina1/video_article_converter
- Nostr Apps 101: https://www.youtube.com/watch?v=Flxa_jkErqE
Output
And now, we have a demonstration of the final result of this tool, with some quick cleaning up. The video we will be using this tool on is titled Nostr Apps 101 by nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 during Nostrasia. The following thread is an analog to the modular articles we are constructing for Alexandria, and I hope it conveys the functionality we want to create in the knowledge space. Note, this tool is the first step! You could use a different prompt that is most appropriate for the specific context of the transcript you are working with, but you can also manually clean up any discrepancies that don't portray the video accurately. You can now view the article on #Alexandria https://next-alexandria.gitcitadel.eu/publication?d=nostr-apps-101
Initially published as chained kind 1's nostr:nevent1qvzqqqqqqypzp5r5hd579v2sszvvzfel677c8dxgxm3skl773sujlsuft64c44ncqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhhyetvv9ujumt0wd68ytnsw43z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309aex2mrp0yh8xmn0wf6zuum0vd5kzmp0qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgc7hglpn
Or view on Coracle https://coracle.social /nevent1qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgcppemhxue69uhkummn9ekx7mp0qgsdqa9md83tz5yqnrqjw07hhkpmfjpkuv9hlh5v8yhu8z274w9dv7qnnq0s3
-
 @ 127d3bf5:466f416f
2025-02-09 03:31:22
@ 127d3bf5:466f416f
2025-02-09 03:31:22I can see why someone would think that buying some other crypto is a reasonable idea for "diversification" or even just for a bit of fun gambling, but it is not.
There are many reasons you should stick to Bitcoin only, and these have been proven correct every cycle. I've outlined these before but will cut and paste below as a summary.
The number one reason, is healthy ethical practice:
- The whole point of Bitcoin is to escape the trappings and flaws of traditional systems. Currency trading and speculative investing is a Tradfi concept, and you will end up back where you started. Sooner or later this becomes obvious to everyone. Bitcoin is the healthy and ethical choice for yourself and everyone else.
But...even if you want to be greedy, hold your horses:
- There is significant risk in wallets, defi, and cefi exchanges. Many have lost all their funds in these through hacks and services getting banned or going bankrupt.
- You get killed in exchange fees even when buying low and selling high. This is effectively a transaction tax which is often hidden (sometimes they don't show the fee, just mark up the exchange rate). Also true on defi exchanges.
- You are up against traders and founders with insider knowledge and much more sophisticated prediction models that will fleece you eventually. You cannot time the market better than they can, and it is their full-time to job to beat you and suck as much liquidity out of you as they can. House always wins.
- Every crypto trade is a taxable event, so you will be taxed on all gains anyway in most countries. So not only are the traders fleecing you, the govt is too.
- It ruins your quality of life constantly checking prices and stressing about making the wrong trade.
The best option, by far, is to slowly DCA into Bitcoin and take this off exchanges into your own custody. In the long run this strategy works out better financially, ethically, and from a quality-of-life perspective. Saving, not trading.
I've been here since 2014 and can personally attest to this.

-
 @ fe32298e:20516265
2025-02-09 01:43:24
@ fe32298e:20516265
2025-02-09 01:43:24Alright, Tabby wouldn't work right with CUDA and it was impossible to troubleshoot anything.
Now we're going to try Twinny.
You'll need:
- Ubuntu 24.04 or some other Linux flavor
- VSCodium
- GPU with enough VRAM to hold your chosen models
- It might work with just a CPU, give it a try!
Install Ollama
Ollama loads the AI models into VRAM (and offloads into RAM if needed) and offers inference through an API. The Ollama install script adds a dedicated
ollamauser and a systemd service so that Ollama starts automatically at boot. Ollama will unload models from memory when idle.curl -fsSL https://ollama.com/install.sh | shConfiguring Remote Ollama
Skip this section if your GPU is on the same machine you're coding from. Ollama and Twinny default to a local configuration.
I'm using Ollama on a separate machine with a decent GPU, so I need to configure it to bind to the network interface instead of
localhostby editing the systemd service:-
Edit the service override file:
systemctl edit ollama.service -
Add this in the top section. It will be merged with the default service file.
[Service] Environment="OLLAMA_HOST=0.0.0.0:11434"Note: I had a problem with Ollama only binding to the
tcp6port, and wasted a lot of time trying to fix it. Check withnetstat -na | grep 11434to see if it only shows tcp6 for port 11434. The workaround for me was using the actual interface IP instead of0.0.0.0. If you do this then you'll need to either setOLLAMA_HOSTin your shell, or specifyOLLAMA_HOST=<hostname>at the start of every ollama command (or it complains that it can't connect to ollama). -
Restart Ollama:
systemctl daemon-reload systemctl restart ollama
Download Models
Ollama manages models by importing them into its own special folders. You can use Ollama to download the files from the Ollama library, or you can import already-downloaded models by creating a Modelfile. Modelfiles define various parameters about the model and it's important to get them set correctly for the best performance so it's probably better to get them from the library, even though it wastes bandwidth downloading them over and over again for all these tools.
You'll want a model for chatting and a model for fill-in-middle (FIM) that does the code completions.
```
Chat model, defaults to 7b with Q4_K_M quant, downloads 4.7 GB
ollama pull qwen2.5-coder
Fill-in-Middle model for code completion, another 4.7 GB
ollama pull qwen2.5-coder:7b-base ```
The RAG/embeddings feature is optional but probably worth using. It needs to run a from local instance of Ollama. The embedding models are very small and run fine on CPU. Most everyone uses
nomic, but Twinny defaults toall-minilm, which is a little smaller.ollama pull all-minilmInstall Twinny
Install the Twinny extension by searching for
twinnyin VSCodium extensions.Look for the Twinny icon on the left side panel and click it to open the Twinny panel. Be careful if you drag it over to the right side: sometimes it may not appear at all. I managed to make it appear by selecting some text and running a Twinny action on it from the context menu.
Twinny assumes you're using a local instance of Ollama. If you want to use a remote instance then you'll need to go into the Manage Twinny providers section (looks like a power plug) and add new providers that point your remote Ollama instance.
These are the settings I'm using for a remote Ollama instance:
Chat provider
- Type:
chat - Provider:
ollama - Protocol:
http - Model Name:
qwen2.5-coder:latest - Hostname: remote hostname
- Port:
11434 - API Path:
/v1(despite what the Twinny docs and Ollama docs say) - API Key: blank
FIM Provider
- Type:
fim - FIM Template:
codeqwen - Provider:
ollama - Protocol:
http - Model Name:
qwen2.5-coder:7b-base - Hostname: remote hostname
- Port:
11434 - API Path:
/api/generate - API Key: blank
Embedding Provider
- Type:
embedding - Provider:
ollama - Protocol:
http - Model Name:
nomic-embed-text - Hostname:
0.0.0.0 - Port:
11434 - API Path:
/api/embed - API Key: blank
Use Twinny
Chat
Select code and it will be used for context in the chat, or right-click selected text to see more options like refactor, write docs, write tests.
Embeddings
Switch over to the Embeddings tab and click Embed documents to use all the documents in your workspace for more context. Type '@' in the chat to reference the entire workspace, ask about specific problems, or specific files in your chat.
Code Completion
Suggested stuff shows up in gray italics at the cursor location. Press
Tabto accept it as a completion. -
 @ eac63075:b4988b48
2024-10-21 08:11:11
@ eac63075:b4988b48
2024-10-21 08:11:11Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.

Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.

The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.

Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.

The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.
 Table reference: Patrick Breyer - Chat Control in 23 September 2024
Table reference: Patrick Breyer - Chat Control in 23 September 2024Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.

The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.

User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.

The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.

Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ ec42c765:328c0600
2024-10-16 08:08:40
@ ec42c765:328c0600
2024-10-16 08:08:40カスタム絵文字とは
任意のオリジナル画像を絵文字のように文中に挿入できる機能です。
また、リアクション(Twitterの いいね のような機能)にもカスタム絵文字を使えます。

カスタム絵文字の対応状況(2024/02/05)

カスタム絵文字を使うためにはカスタム絵文字に対応したクライアントを使う必要があります。
※表は一例です。クライアントは他にもたくさんあります。
使っているクライアントが対応していない場合は、クライアントを変更する、対応するまで待つ、開発者に要望を送る(または自分で実装する)などしましょう。
対応クライアント
ここではnostterを使って説明していきます。
準備
カスタム絵文字を使うための準備です。
- Nostrエクステンション(NIP-07)を導入する
- 使いたいカスタム絵文字をリストに登録する
Nostrエクステンション(NIP-07)を導入する
Nostrエクステンションは使いたいカスタム絵文字を登録する時に必要になります。
また、環境(パソコン、iPhone、androidなど)によって導入方法が違います。
Nostrエクステンションを導入する端末は、実際にNostrを閲覧する端末と違っても構いません(リスト登録はPC、Nostr閲覧はiPhoneなど)。
Nostrエクステンション(NIP-07)の導入方法は以下のページを参照してください。
ログイン拡張機能 (NIP-07)を使ってみよう | Welcome to Nostr! ~ Nostrをはじめよう! ~
少し面倒ですが、これを導入しておくとNostr上の様々な場面で役立つのでより快適になります。
使いたいカスタム絵文字をリストに登録する
以下のサイトで行います。
右上のGet startedからNostrエクステンションでログインしてください。
例として以下のカスタム絵文字を導入してみます。
実際より絵文字が少なく表示されることがありますが、古い状態のデータを取得してしまっているためです。その場合はブラウザの更新ボタンを押してください。

- 右側のOptionsからBookmarkを選択

これでカスタム絵文字を使用するためのリストに登録できます。
カスタム絵文字を使用する
例としてブラウザから使えるクライアント nostter から使用してみます。
nostterにNostrエクステンションでログイン、もしくは秘密鍵を入れてログインしてください。
文章中に使用
- 投稿ボタンを押して投稿ウィンドウを表示
- 顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択
- : 記号に挟まれたアルファベットのショートコードとして挿入される

この状態で投稿するとカスタム絵文字として表示されます。
カスタム絵文字対応クライアントを使っている他ユーザーにもカスタム絵文字として表示されます。
対応していないクライアントの場合、ショートコードのまま表示されます。

ショートコードを直接入力することでカスタム絵文字の候補が表示されるのでそこから選択することもできます。

リアクションに使用
- 任意の投稿の顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択

カスタム絵文字リアクションを送ることができます。

カスタム絵文字を探す
先述したemojitoからカスタム絵文字を探せます。
例えば任意のユーザーのページ emojito ロクヨウ から探したり、 emojito Browse all からnostr全体で最近作成、更新された絵文字を見たりできます。
また、以下のリンクは日本語圏ユーザーが作ったカスタム絵文字を集めたリストです(2024/06/30)
※漏れがあるかもしれません
各絵文字セットにあるOpen in emojitoのリンクからemojitoに飛び、使用リストに追加できます。
以上です。
次:Nostrのカスタム絵文字の作り方
Yakihonneリンク Nostrのカスタム絵文字の作り方
Nostrリンク nostr:naddr1qqxnzdesxuunzv358ycrgveeqgswcsk8v4qck0deepdtluag3a9rh0jh2d0wh0w9g53qg8a9x2xqvqqrqsqqqa28r5psx3
仕様
-
 @ 16d11430:61640947
2025-02-09 01:03:30
@ 16d11430:61640947
2025-02-09 01:03:30As fiat currencies continue their slow-motion collapse worldwide, a disturbing pattern is emerging—food security is deteriorating, marked by frequent outbreaks of avian flu, livestock diseases, and supply chain disruptions. While mainstream narratives often blame climate change or random chance, a deeper look reveals that these crises are symptoms of a decaying financial system.
Food shortages, increasing corporate monopolization of agriculture, and government mismanagement are not random events. They are predictable consequences of monetary debasement, supply chain stress, and regulatory capture. Let’s break down how the collapse of fiat money is driving the current food crisis and why things are likely to get worse.
- Early Signs: Inflation and the Cost of Farming Soar
The first cracks in the food supply system appear when inflation begins eating into farmers’ margins. Over the past few years, fertilizer prices have skyrocketed, fuel costs remain volatile, and animal feed has become more expensive due to disrupted global trade.
Example: The 2022 Fertilizer Crisis – As the U.S. and European governments sanctioned Russia, a key global supplier of potash and ammonia (key fertilizer ingredients), prices surged. Farmers in Africa, Asia, and Latin America struggled to afford these inputs, reducing food production.
Egg Prices & Avian Flu – In 2023, egg prices doubled in the U.S. and Europe, exacerbated by avian flu culling millions of hens. However, inflation played a bigger role—higher costs for feed, transport, and farm maintenance made it impossible for smaller producers to compete.
Corporate Centralization – As inflation drives small farmers out of business, giant agribusinesses like Cargill, JBS, and Tyson gain more control, further consolidating the supply chain.
At this stage, the system still functions, but food prices increase, and warning signs emerge.
- Mid-Stage: Supply Chains Crack & Regulatory Failures Accelerate Outbreaks
As inflation worsens, government policies and systemic inefficiencies accelerate decay. Regulations intended to "protect" the market often do the opposite—causing supply shocks and increasing food insecurity.
Avian Flu as a Convenient Cover? – Since 2022, millions of chickens, turkeys, and ducks have been culled globally due to "avian flu outbreaks." The strange part? Many cases are based on PCR tests with high false positives rather than confirmed clinical symptoms. Some suspect regulatory agencies are exaggerating the crisis to justify price hikes and consolidate control.
U.S. Cattle Mysteriously Falling Sick – Reports surfaced in early 2024 of large numbers of cattle experiencing spontaneous respiratory illness and reproductive failures. The USDA and FDA blame viruses, but critics point to contaminated mRNA vaccines or corporate feed modifications.
Dutch Farmers vs. The State – In the Netherlands, one of Europe’s largest food producers, the government attempted to force thousands of farmers to sell their land under the guise of "nitrogen reduction." Many believe this is an effort to centralize control over food production.
At this stage, outbreaks become more frequent—not just due to biological causes, but because of poor regulation, centralized control, and financial stress leading to cost-cutting in food safety.
- Late-Stage: Hyperinflation, Panic, and Rationing
Once inflation turns into hyperinflation, food becomes a political weapon. Governments respond with price controls, forced rationing, and market interventions that make things worse.
Argentina & Venezuela’s Food Rationing – In nations experiencing hyperinflation, like Argentina and Venezuela, supermarket shelves are empty, and the black market determines real prices. Government-issued food ration cards fail to provide reliable access.
French Farmers Revolt Over Regulations & Costs – In 2024, French farmers blocked highways in protest against tax hikes, environmental regulations, and soaring costs. The EU’s green policies, combined with inflation, made food production unviable.
Egg Shortages in the UK – The UK government urged people to eat fewer eggs and replace them with lab-grown alternatives as supermarkets struggled to restock due to avian flu and Brexit-related trade issues.
At this point, government incompetence and corporate profiteering worsen food insecurity, leading to riots, black markets, and authoritarian responses.
- Final Collapse: Mass Starvation or Parallel Systems
As fiat systems implode, parallel markets emerge. People turn to barter, Bitcoin-based trade, and decentralized farming networks to survive.
Bitcoin for Beef – In Argentina and El Salvador, some ranchers have started accepting Bitcoin for direct meat sales, bypassing the banking system entirely.
Local Food Networks Grow – In places where trust in fiat money collapses, local food networks, permaculture movements, and barter systems gain popularity.
Lab-Grown & Insect Protein Push – Meanwhile, governments and billionaires like Bill Gates push for synthetic meat and insect-based diets, claiming they are "sustainable" while continuing policies that destroy natural farming.
At this stage, centralized systems are collapsing, but decentralized alternatives emerge—offering a path forward for those willing to adapt.
The Solution: Decentralization & Bitcoin-Based Trade
The fiat food system is failing because it is built on debt, leverage, and market manipulation. To ensure food security, we must return to decentralized, sound-money solutions.
Bitcoin as a Trade Standard – Farmers using Bitcoin escape capital controls and currency depreciation, ensuring fair trade.
Regenerative Agriculture & Local Food Systems – Returning to small-scale, diversified farming reduces the risk of mass outbreaks.
Self-Sovereignty Over Food – Growing your own food, supporting local farmers, and rejecting centralized food policies is the only way to break free from the collapsing system.
Conclusion: Recognizing the Signs Before It's Too Late
The rapid spread of avian flu, livestock diseases, and farm shutdowns are not random events. They are early warning signs of systemic decay in the fiat economy. As governments print money and impose short-sighted regulations, food security worsens.
The best way forward is decentralization—of money, farming, and trade. The collapse of fiat will bring hardship, but those who understand the game and prepare accordingly will thrive.
-
 @ c4f5e7a7:8856cac7
2024-09-27 08:20:16
@ c4f5e7a7:8856cac7
2024-09-27 08:20:16Best viewed on Habla, YakiHonne or Highlighter.
TL;DR
This article explores the links between public, community-driven data sources (such as OpenStreetMap) and private, cryptographically-owned data found on networks such as Nostr.
The following concepts are explored:
- Attestations: Users signalling to their social graph that they believe something to be true by publishing Attestations. These social proofs act as a decentralised verification system that leverages your web-of-trust.
- Proof of Place: An oracle-based system where physical letters are sent to real-world locations, confirming the corresponding digital ownership via cryptographic proofs. This binds physical locations in meatspace with their digital representations in the Nostrverse.
- Check-ins: Foursquare-style check-ins that can be verified using attestations from place owners, ensuring authenticity. This approach uses web-of-trust to validate check-ins and location ownership over time.
The goal is to leverage cryptographic ownership where necessary while preserving the open, collaborative nature of public data systems.
Open Data in a public commons has a place and should not be thrown out with the Web 2.0 bathwater.
Cognitive Dissonance
Ever since discovering Nostr in August of 2022 I've been grappling with how BTC Map - a project that helps bitcoiners find places to spend sats - should most appropriately use this new protocol.
I am assuming, dear reader, that you are somewhat familiar with Nostr - a relatively new protocol for decentralised identity and communication. If you don’t know your nsec from your npub, please take some time to read these excellent posts: Nostr is Identity for the Internet and The Power of Nostr by @max and @lyn, respectively. Nostr is so much more than a short-form social media replacement.
The social features (check-ins, reviews, etc.) that Nostr unlocks for BTC Map are clear and exciting - all your silos are indeed broken - however, something fundamental has been bothering me for a while and I think it comes down to data ownership.
For those unfamiliar, BTC Map uses OpenStreetMap (OSM) as its main geographic database. OSM is centred on the concept of a commons of objectively verifiable data that is maintained by a global community of volunteer editors; a Wikipedia for maps. There is no data ownership; the data is free (as in freedom) and anyone can edit anything. It is the data equivalent of FOSS (Free and Open Source Software) - FOSD if you will, but more commonly referred to as Open Data.
In contrast, Notes and Other Stuff on Nostr (Places in this cartographic context) are explicitly owned by the controller of the private key. These notes are free to propagate, but they are owned.
How do we reconcile the decentralised nature of Nostr, where data is cryptographically owned by individuals, with the community-managed data commons of OpenStreetMap, where no one owns the data?
Self-sovereign Identity
Before I address this coexistence question, I want to talk a little about identity as it pertains to ownership. If something is to be owned, it has to be owned by someone or something - an identity.
All identities that are not self-sovereign are, by definition, leased to you by a 3rd party. You rent your Facebook identity from Meta in exchange for your data. You rent your web domain from your DNS provider in exchange for your money.
Taken to the extreme, you rent your passport from your Government in exchange for your compliance. You are you at the pleasure of others. Where Bitcoin separates money from the state; Nostr separates identity from the state.
Or, as @nvk said recently: "Don't build your house on someone else's land.".
https://i.nostr.build/xpcCSkDg3uVw0yku.png
While we’ve had the tools for self-sovereign digital identity for decades (think PGP keys or WebAuthN), we haven't had the necessary social use cases nor the corresponding social graph to elevate these identities to the mainstream. Nostr fixes this.
Nostr is PGP for the masses and will take cryptographic identities mainstream.
Full NOSTARD?
Returning to the coexistence question: the data on OpenStreetMap isn’t directly owned by anyone, even though the physical entities the data represents might be privately owned. OSM is a data commons.
We can objectively agree on the location of a tree or a fire hydrant without needing permission to observe and record it. Sure, you could place a tree ‘on Nostr’, but why should you? Just because something can be ‘on Nostr’ doesn’t mean it should be.
https://i.nostr.build/s3So2JVAqoY4E1dI.png
There might be a dystopian future where we can't agree on what a tree is nor where it's located, but I hope we never get there. It's at this point we'll need a Wikifreedia variant of OpenStreetMap.
While integrating Nostr identities into OpenStreetMap would be valuable, the current OSM infrastructure, tools, and community already provide substantial benefits in managing this data commons without needing to go NOSTR-native - there's no need to go Full NOSTARD. H/T to @princeySOV for the original meme.
https://i.nostr.build/ot9jtM5cZtDHNKWc.png
So, how do we appropriately blend cryptographically owned data with the commons?
If a location is owned in meatspace and it's useful to signal that ownership, it should also be owned in cyberspace. Our efforts should therefore focus on entities like businesses, while allowing the commons to manage public data for as long as it can successfully mitigate the tragedy of the commons.
The remainder of this article explores how we can:
- Verify ownership of a physical place in the real world;
- Link that ownership to the corresponding digital place in cyberspace.
As a side note, I don't see private key custodianship - or, even worse, permissioned use of Places signed by another identity's key - as any more viable than the rented identities of Web 2.0.
And as we all know, the Second Law of Infodynamics (no citation!) states that:
"The total amount of sensitive information leaked will always increase over time."
This especially holds true if that data is centralised.
Not your keys, not your notes. Not your keys, not your identity.
Places and Web-of-Trust
@Arkinox has been leading the charge on the Places NIP, introducing Nostr notes (kind 37515) that represent physical locations. The draft is well-crafted, with bonus points for linking back to OSM (and other location repositories) via NIP-73 - External Content IDs (championed by @oscar of @fountain).
However, as Nostr is permissionless, authenticity poses a challenge. Just because someone claims to own a physical location on the Internet doesn’t necessarily mean they have ownership or control of that location in the real world.
Ultimately, this problem can only be solved in a decentralised way by using Web-of-Trust - using your social graph and the perspectives of trusted peers to inform your own perspective. In the context of Places, this requires your network to form a view on which digital identity (public key / npub) is truly the owner of a physical place like your local coffee shop.
This requires users to:
- Verify the owner of a Place in cyberspace is the owner of a place in meatspace.
- Signal this verification to their social graph.
Let's look at the latter idea first with the concept of Attestations ...
Attestations
A way to signal to your social graph that you believe something to be true (or false for that matter) would be by publishing an Attestation note. An Attestation note would signify to your social graph that you think something is either true or false.
Imagine you're a regular at a local coffee shop. You publish an Attestation that says the shop is real and the owner behind the Nostr public key is who they claim to be. Your friends trust you, so they start trusting the shop's digital identity too.
However, attestations applied to Places are just a single use case. The attestation concept could be more widely applied across Nostr in a variety of ways (key rotation, identity linking, etc).
Here is a recent example from @lyn that would carry more signal if it were an Attestation:
https://i.nostr.build/lZAXOEwvRIghgFY4.png
Parallels can be drawn between Attestations and transaction confirmations on the Bitcoin timechain; however, their importance to you would be weighted by clients and/or Data Vending Machines in accordance with:
- Your social graph;
- The type or subject of the content being attested and by whom;
- Your personal preferences.
They could also have a validity duration to be temporally bound, which would be particularly useful in the case of Places.
NIP-25 (Reactions) do allow for users to up/downvote notes with optional content (e.g., emojis) and could work for Attestations, but I think we need something less ambiguous and more definitive.
‘This is true’ resonates more strongly than ‘I like this.’.
https://i.nostr.build/s8NIG2kXzUCLcoax.jpg
There are similar concepts in the Web 3 / Web 5 world such as Verified Credentials by tdb. However, Nostr is the Web 3 now and so wen Attestation NIP?
https://i.nostr.build/Cb047NWyHdJ7h5Ka.jpg
That said, I have seen @utxo has been exploring ‘smart contracts’ on nostr and Attestations may just be a relatively ‘dumb’ subset of the wider concept Nostr-native scripting combined with web-of-trust.
Proof of Place
Attestations handle the signalling of your truth, but what about the initial verification itself?
We already covered how this ultimately has to be derived from your social graph, but what if there was a way to help bootstrap this web-of-trust through the use of oracles? For those unfamiliar with oracles in the digital realm, they are simply trusted purveyors of truth.
Introducing Proof of Place, an out–of-band process where an oracle (such as BTC Map) would mail - yes physically mail- a shared secret to the address of the location being claimed in cyberspace. This shared secret would be locked to the public key (npub) making the claim, which, if unlocked, would prove that the associated private key (nsec) has physical access to the location in meatspace.
One way of doing this would be to mint a 1 sat cashu ecash token locked to the npub of the claimant and mail it to them. If they are able to redeem the token then they have cryptographically proven that they have physical access to the location.
Proof of Place is really nothing more than a weighted Attestation. In a web-of-trust Nostrverse, an oracle is simply a npub (say BTC Map) that you weigh heavily for its opinion on a given topic (say Places).
In the Bitcoin world, Proof of Work anchors digital scarcity in cyberspace to physical scarcity (energy and time) in meatspace and as @Gigi says in PoW is Essential:
"A failure to understand Proof of Work, is a failure to understand Bitcoin."
In the Nostrverse, Proof of Place helps bridge the digital and physical worlds.
@Gigi also observes in Memes vs The World that:
"In Bitcoin, the map is the territory. We can infer everything we care about by looking at the map alone."
https://i.nostr.build/dOnpxfI4u7EL2v4e.png
This isn’t true for Nostr.
In the Nostrverse, the map IS NOT the territory. However, Proof of Place enables us to send cryptographic drones down into the physical territory to help us interpret our digital maps. 🤯
Check-ins
Although not a draft NIP yet, @Arkinox has also been exploring the familiar concept of Foursquare-style Check-ins on Nostr (with kind 13811 notes).
For the uninitiated, Check-ins are simply notes that signal the publisher is at a given location. These locations could be Places (in the Nostr sense) or any other given digital representation of a location for that matter (such as OSM elements) if NIP-73 - External Content IDs are used.
Of course, not everyone will be a Check-in enjoyooor as the concept will not sit well with some people’s threat models and OpSec practices.
Bringing Check-ins to Nostr is possible (as @sebastix capably shows here), but they suffer the same authenticity issues as Places. Just because I say I'm at a given location doesn't mean that I am.
Back in the Web 2.0 days, Foursquare mitigated this by relying on the GPS position of the phone running their app, but this is of course spoofable.
How should we approach Check-in verifiability in the Nostrverse? Well, just like with Places, we can use Attestations and WoT. In the context of Check-ins, an Attestation from the identity (npub) of the Place being checked-in to would be a particularly strong signal. An NFC device could be placed in a coffee shop and attest to check-ins without requiring the owner to manually intervene - I’m sure @blackcoffee and @Ben Arc could hack something together over a weekend!
Check-ins could also be used as a signal for bonafide Place ownership over time.
Summary: Trust Your Bros
So, to recap, we have:
Places: Digital representations of physical locations on Nostr.
Check-ins: Users signalling their presence at a location.
Attestations: Verifiable social proofs used to confirm ownership or the truth of a claim.
You can visualise how these three concepts combine in the diagram below:
https://i.nostr.build/Uv2Jhx5BBfA51y0K.jpg
And, as always, top right trumps bottom left! We have:
Level 0 - Trust Me Bro: Anyone can check-in anywhere. The Place might not exist or might be impersonating the real place in meatspace. The person behind the npub may not have even been there at all.
Level 1 - Definitely Maybe Somewhere: This category covers the middle-ground of ‘Maybe at a Place’ and ‘Definitely Somewhere’. In these examples, you are either self-certifying that you have checked-in at an Attested Place or you are having others attest that you have checked-in at a Place that might not even exist IRL.
Level 2 - Trust Your Bros: An Attested Check-in at an Attested Place. Your individual level of trust would be a function of the number of Attestations and how you weigh them within your own social graph.
https://i.nostr.build/HtLAiJH1uQSTmdxf.jpg
Perhaps the gold standard (or should that be the Bitcoin standard?) would be a Check-in attested by the owner of the Place, which in itself was attested by BTC Map?
Or perhaps not. Ultimately, it’s the users responsibility to determine what they trust by forming their own perspective within the Nostrverse powered by web-of-trust algorithms they control. ‘Trust Me Bro’ or ‘Trust Your Bros’ - you decide.
As we navigate the frontier of cryptographic ownership and decentralised data, it’s up to us to find the balance between preserving the Open Data commons and embracing self-sovereign digital identities.
Thanks
With thanks to Arkinox, Avi, Ben Gunn, Kieran, Blackcoffee, Sebastix, Tomek, Calle, Short Fiat, Ben Weeks and Bitcoms for helping shape my thoughts and refine content, whether you know it or not!
-
 @ 09fbf8f3:fa3d60f0
2024-09-10 13:21:23
@ 09fbf8f3:fa3d60f0
2024-09-10 13:21:23由于gmail在中国被防火墙拦截了,无法打开,不想错过邮件通知。
通过自建ntfy接受gmail邮件通知。 怎么自建ntfy,后面再写。
2024年08月13日更新:
修改不通过添加邮件标签来标记已经发送的通知,通过Google Sheets来记录已经发送的通知。
为了不让Google Sheets文档的内容很多,导致文件变大,用脚本自动清理一个星期以前的数据。
准备工具
- Ntfy服务
- Google Script
- Google Sheets
操作步骤
- 在Ntfy后台账号,设置访问令牌。
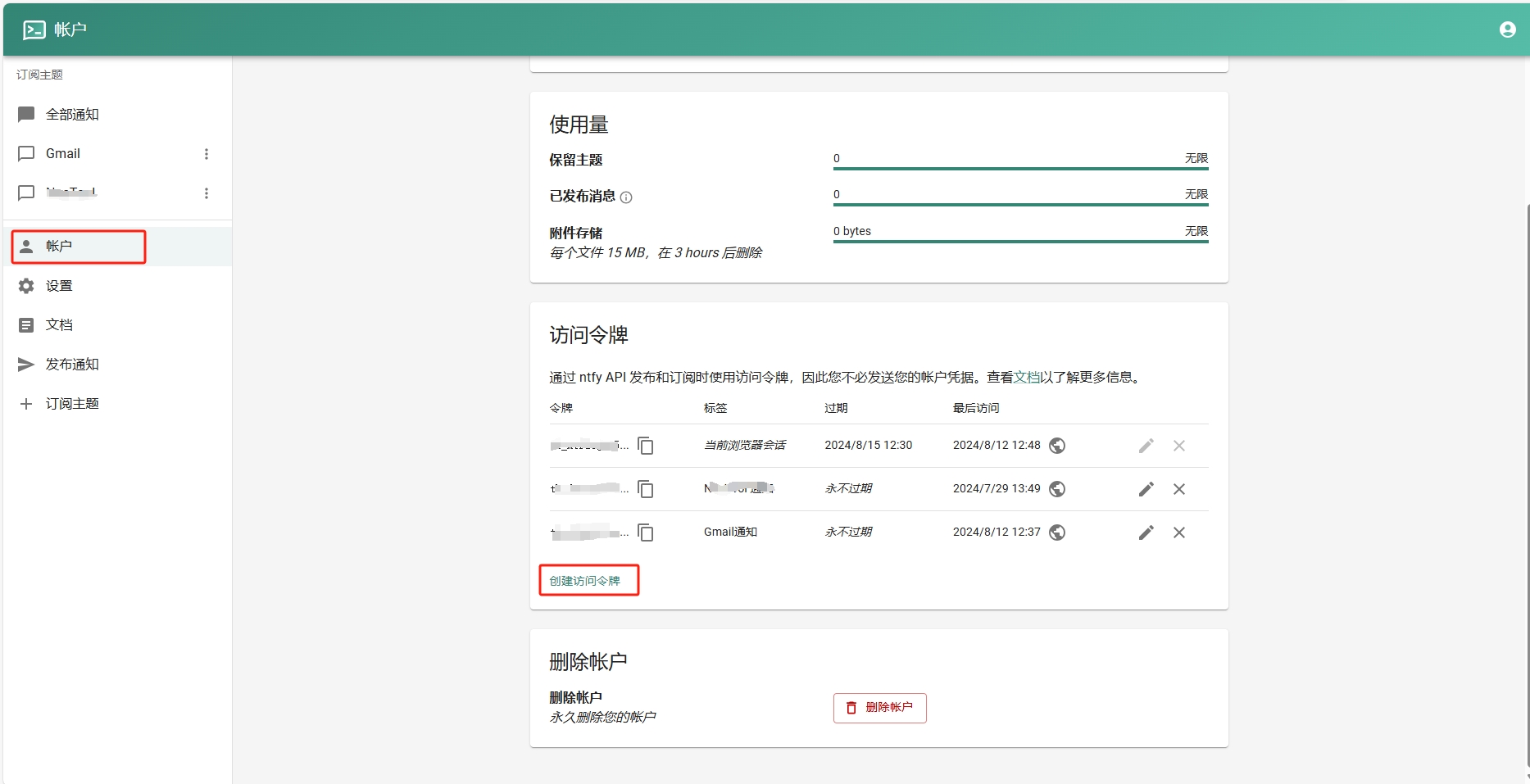
- 添加订阅主题。
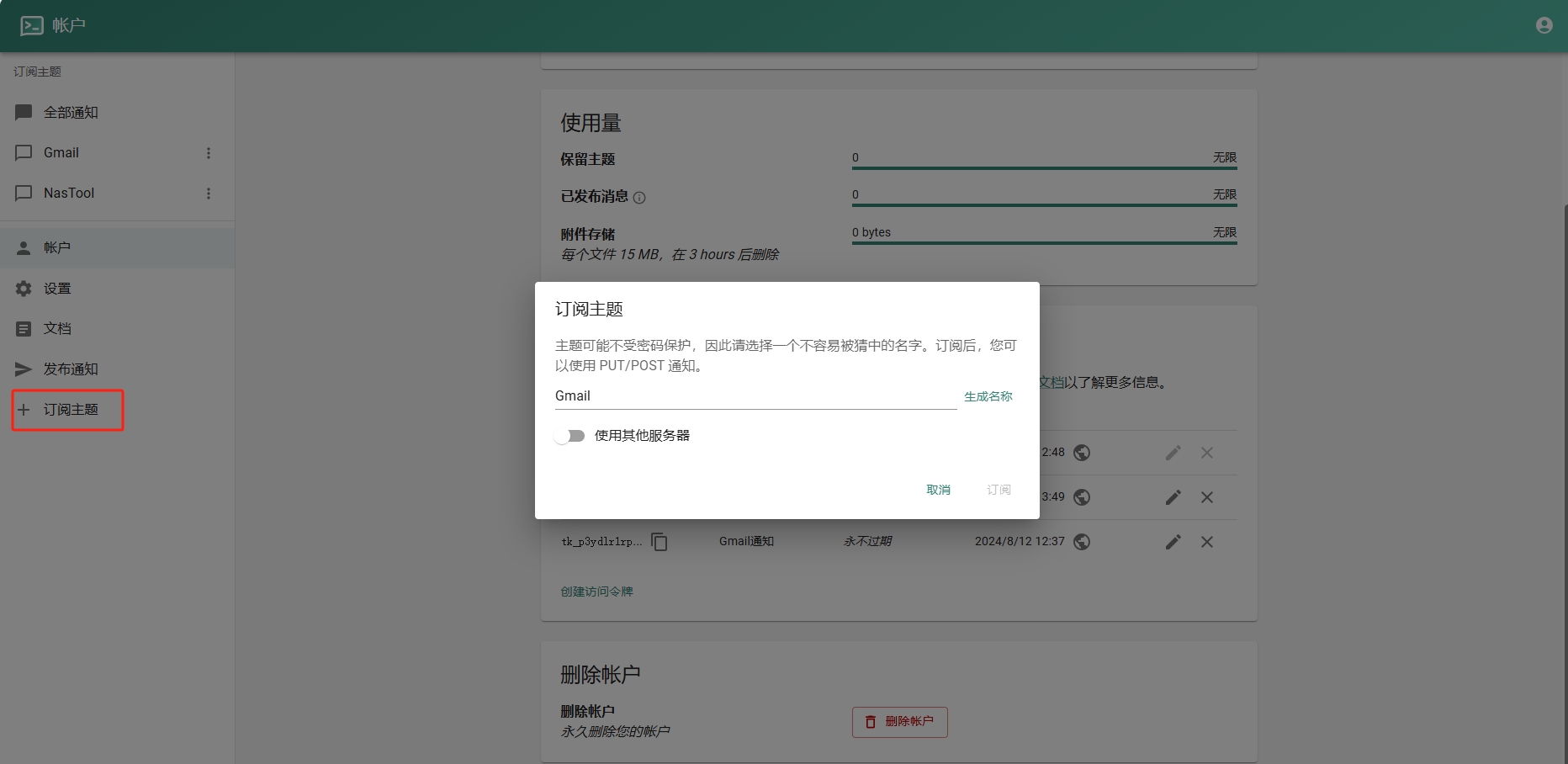
- 进入Google Sheets创建一个表格.记住id,如下图:
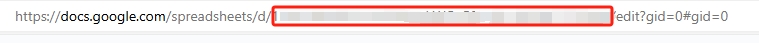
- 进入Google Script创建项目。填入以下代码(注意填入之前的ntfy地址和令牌):
```javascript function checkEmail() { var sheetId = "你的Google Sheets id"; // 替换为你的 Google Sheets ID var sheet = SpreadsheetApp.openById(sheetId).getActiveSheet();
// 清理一星期以前的数据 cleanOldData(sheet, 7 * 24 * 60); // 保留7天(即一周)内的数据
var sentEmails = getSentEmails(sheet);
var threads = GmailApp.search('is:unread'); Logger.log("Found threads: " + threads.length);
if (threads.length === 0) return;
threads.forEach(function(thread) { var threadId = thread.getId();
if (!sentEmails.includes(threadId)) { thread.getMessages().forEach(sendNtfyNotification); recordSentEmail(sheet, threadId); }}); }
function sendNtfyNotification(email) { if (!email) { Logger.log("Email object is undefined or null."); return; }
var message = `发件人: ${email.getFrom() || "未知发件人"} 主题: ${email.getSubject() || "无主题"}
内容: ${email.getPlainBody() || "无内容"}`;
var url = "https://你的ntfy地址/Gmail"; var options = { method: "post", payload: message, headers: { Authorization: "Bearer Ntfy的令牌" }, muteHttpExceptions: true };
try { var response = UrlFetchApp.fetch(url, options); Logger.log("Response: " + response.getContentText()); } catch (e) { Logger.log("Error: " + e.message); } }
function getSentEmails(sheet) { var data = sheet.getDataRange().getValues(); return data.map(row => row[0]); // Assuming email IDs are stored in the first column }
function recordSentEmail(sheet, threadId) { sheet.appendRow([threadId, new Date()]); }
function cleanOldData(sheet, minutes) { var now = new Date(); var thresholdDate = new Date(now.getTime() - minutes * 60 * 1000); // 获取X分钟前的时间
var data = sheet.getDataRange().getValues(); var rowsToDelete = [];
data.forEach(function(row, index) { var date = new Date(row[1]); // 假设日期保存在第二列 if (date < thresholdDate) { rowsToDelete.push(index + 1); // 存储要删除的行号 } });
// 逆序删除(从最后一行开始删除,以避免行号改变) rowsToDelete.reverse().forEach(function(row) { sheet.deleteRow(row); }); }
```
5.Google Script是有限制的不能频繁调用,可以设置五分钟调用一次。如图:
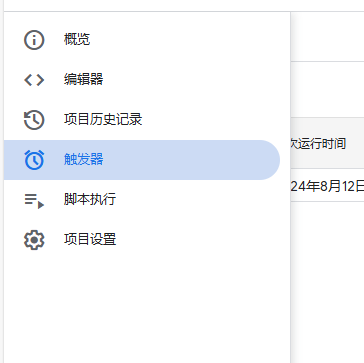
结尾
本人不会代码,以上代码都是通过chatgpt生成的。经过多次修改,刚开始会一直发送通知,后面修改后将已发送的通知放到一个“通知”的标签里。后续不会再次发送通知。
如需要发送通知后自动标记已读,可以把代码复制到chatgpt给你写。
-
 @ 7460b7fd:4fc4e74b
2024-09-05 08:37:48
@ 7460b7fd:4fc4e74b
2024-09-05 08:37:48请看2014年王兴的一场思维碰撞,视频27分钟开始
最后,一个当时无法解决的点:丢失
-
 @ 4523be58:ba1facd0
2024-05-28 11:05:17
@ 4523be58:ba1facd0
2024-05-28 11:05:17NIP-116
Event paths
Description
Event kind
30079denotes an event defined by its event path rather than its event kind.The event directory path is included in the event path, specified in the event's
dtag. For example, an event path might beuser/profile/name, whereuser/profileis the directory path.Relays should parse the event directory from the event path
dtag and index the event by it. Relays should support "directory listing" of kind30079events using the#ffilter, such as{"#f": ["user/profile"]}.For backward compatibility, the event directory should also be saved in the event's
ftag (for "folder"), which is already indexed by some relay implementations, and can be queried using the#ffilter.Event content should be a JSON-encoded value. An empty object
{}signifies that the entry at the event path is itself a directory. For example, when savinguser/profile/name:Bob, you should also saveuser/profile:{}so the subdirectory can be listed underuser.In directory names, slashes should be escaped with a double slash.
Example
Event
json { "tags": [ ["d", "user/profile/name"], ["f", "user/profile"] ], "content": "\"Bob\"", "kind": 30079, ... }Query
json { "#f": ["user/profile"], "authors": ["[pubkey]"] }Motivation
To make Nostr an "everything app," we need a sustainable way to support new kinds of applications. Browsing Nostr data by human-readable nested directories and paths rather than obscure event kind numbers makes the data more manageable.
Numeric event kinds are not sustainable for the infinite number of potential applications. With numeric event kinds, developers need to find an unused number for each new application and announce it somewhere, which is cumbersome and not scalable.
Directories can also replace monolithic list events like follow lists or profile details. You can update a single directory entry such as
user/profile/nameorgroups/follows/[pubkey]without causing an overwrite of the whole profile or follow list when your client is out-of-sync with the most recent list version, as often happens on Nostr.Using
d-tagged replaceable events for reactions, such as{tags: [["d", "reactions/[eventId]"]], content: "\"👍\"", kind: 30079, ...}would make un-reacting trivial: just publish a new event with the samedtag and an empty content. Toggling a reaction on and off would not cause a flurry of new reaction & delete events that all need to be persisted.Implementations
- Relays that support tag-replaceable events and indexing by arbitrary tags (in this case
f) already support this feature. - IrisDB client side library: treelike data structure with subscribable nodes.
https://github.com/nostr-protocol/nips/pull/1266
- Relays that support tag-replaceable events and indexing by arbitrary tags (in this case
-
 @ b60c3e76:c9d0f46e
2024-05-15 10:08:47
@ b60c3e76:c9d0f46e
2024-05-15 10:08:47KRIS menjamin semua golongan masyarakat mendapatkan perlakuan sama dari rumah sakit, baik pelayanan medis maupun nonmedis.
Demi memberikan peningkatan kualitas layanan kesehatan kepada masyarakat, pemerintah baru saja mengeluarkan Peraturan Presiden (Perpres) nomor 59 tahun 2024 tentang Jaminan Kesehatan. Melalui perpres itu, Presiden Joko Widodo (Jokowi) telah menghapus perbedaan kelas layanan 1, 2, dan 3 dalam Badan Penyelenggara Jaminan Sosial atau BPJS Kesehatan.
Layanan berbasis kelas itu diganti dengan KRIS (Kelas Rawat Inap Standar). Berkaitan dengan lahirnya Perpres 59/2024 tentang Perubahan Ketiga atas Perpres 82/2018 tentang Jaminan Kesehatan, Presiden Joko Widodo telah memerintahkan seluruh rumah sakit yang bekerja sama dengan BPJS Kesehatan melaksanakannya.
Kebijakan baru itu mulai berlaku per 8 Mei 2024 dan paling lambat 30 Juni 2025. Dalam jangka waktu tersebut, rumah sakit dapat menyelenggarakan sebagian atau seluruh pelayanan rawat inap berdasarkan KRIS sesuai dengan kemampuan rumah sakit.
Lantas apa yang menjadi pembeda dari sisi layanan dengan layanan rawat inap sesuai Perpres 59/2024? Dahulu sistem layanan rawat BPJS Kesehatan dibagi berdasarkan kelas yang dibagi masing-masing kelas 1, 2, dan 3. Namun, melalui perpres, layanan kepada masyarakat tidak dibedakan lagi.
Pelayanan rawat inap yang diatur dalam perpres itu--dikenal dengan nama KRIS—menjadi sistem baru yang digunakan dalam pelayanan rawat inap BPJS Kesehatan di rumah sakit-rumah sakit. Dengan KRIS, semua golongan masyarakat akan mendapatkan perlakuan yang sama dari rumah sakit, baik dalam hal pelayanan medis maupun nonmedis.
Dengan lahirnya Perpres 59/2024, tarif iuran BPJS Kesehatan pun juga akan berubah. Hanya saja, dalam Perpres itu belum dicantumkan secara rinci ihwal besar iuran yang baru. Besaran iuran baru BPJS Kesehatan itu sesuai rencana baru ditetapkan pada 1 Juli 2025.
“Penetapan manfaat, tarif, dan iuran sebagaimana dimaksud ditetapkan paling lambat tanggal 1 Juli 2025,” tulis aturan tersebut, dikutip Senin (13/5/2024).
Itu artinya, iuran BPJS Kesehatan saat ini masih sama seperti sebelumnya, yakni sesuai dengan kelas yang dipilih. Namun perpres itu tetap berlaku sembari menanti lahirnya peraturan lanjutan dari perpres tersebut.
Kesiapan Rumah Sakit
Berkaitan dengan lahirnya kebijakan layanan kesehatan tanpa dibedakan kelas lagi, Kementerian Kesehatan (Kemenkes) menegaskan mayoritas rumah sakit di Indonesia siap untuk menjalankan layanan KRIS untuk pasien BPJS Kesehatan.
Kesiapan itu diungkapkan oleh Dirjen Pelayanan Kesehatan Kemenkes Azhar Jaya. “Survei kesiapan RS terkait KRIS sudah dilakukan pada 2.988 rumah sakit dan yang sudah siap menjawab isian 12 kriteria ada sebanyak 2.233 rumah sakit,” ujar Azhar.
Sebagai informasi, KRIS adalah pengganti layanan Kelas 1, 2, dan 3 BPJS Kesehatan yang bertujuan untuk memberikan layanan kesehatan secara merata tanpa melihat besaran iurannya.
Melalui KRIS, rumah sakit perlu menyiapkan sarana dan prasarana sesuai dengan 12 kriteria kelas rawat inap standar secara bertahap. Apa saja ke-12 kriteria KRIS itu?
Sesuai bunyi Pasal 46A Perpres 59/2024, disyaratkan kriteria fasilitas perawatan dan pelayanan rawat inap KRIS meliputi komponen bangunan yang digunakan tidak boleh memiliki tingkat porositas yang tinggi serta terdapat ventilasi udara dan kelengkapan tidur.
Demikian pula soal pencahayaan ruangan. Perpres itu juga mengatur pencahayaan ruangan buatan mengikuti kriteria standar 250 lux untuk penerangan dan 50 lux untuk pencahayaan tidur, temperature ruangan 20--26 derajat celcius.
Tidak hanya itu, layanan rawat inap berdasarkan perpres itu mensyaratkan fasilitas layanan yang membagi ruang rawat berdasarkan jenis kelamin pasien, anak atau dewasa, serta penyakit infeksi atau noninfeksi.
Selain itu, kriteria lainnya adalah keharusan bagi penyedia layanan untuk mempertimbangkan kepadatan ruang rawat dan kualitas tempat tidur, penyediaan tirai atau partisi antartempat tidur, kamar mandi dalam ruangan rawat inap yang memenuhi standar aksesibilitas, dan menyediakan outlet oksigen.
Selain itu, kelengkapan tempat tidur berupa adanya dua kotak kontak dan nurse call pada setiap tempat tidur dan adanya nakas per tempat tidur. Kepadatan ruang rawat inap maksimal empat tempat tidur dengan jarak antara tepi tempat tidur minimal 1,5 meter.
Tirai/partisi dengan rel dibenamkan menempel di plafon atau menggantung. Kamar mandi dalam ruang rawat inap serta kamar mandi sesuai dengan standar aksesibilitas dan outlet oksigen.
Azhar menjamin, Kemenkes akan menjalankan hal tersebut sesuai dengan tupoksi yang ada. “Tentu saja kami akan bekerja sama dengan BPJS Kesehatan dalam implementasi dan pengawasannya di lapangan,” ujar Azhar.
Berkaitan dengan perpres jaminan kesehatan itu, Direktur Utama BPJS Kesehatan Ghufron Mukti menilai, perpres tersebut berorientasi pada penyeragaman kelas rawat inap yang mengacu pada 12 kriteria. "Bahwa perawatan ada kelas rawat inap standar dengan 12 kriteria, untuk peserta BPJS, maka sebagaimana sumpah dokter tidak boleh dibedakan pemberian pelayan medis atas dasar suku, agama, status sosial atau beda iurannya," ujarnya.
Jika ada peserta ingin dirawat pada kelas yang lebih tinggi, kata Ghufron, maka diperbolehkan selama hal itu dipengaruhi situasi nonmedis. Hal itu disebutkan dalam Pasal 51 Perpres Jaminan Kesehatan diatur ketentuan naik kelas perawatan.
Menurut pasal tersebut, naik kelas perawatan dilakukan dengan cara mengikuti asuransi kesehatan tambahan atau membayar selisih antara biaya yang dijamin oleh BPJS Kesehatan dengan biaya yang harus dibayar akibat peningkatan pelayanan.
Selisih antara biaya yang dijamin oleh BPJS Kesehatan dengan biaya pelayanan dapat dibayar oleh peserta bersangkutan, pemberi kerja, atau asuransi kesehatan tambahan.
Ghufron Mukti juga mengimbau pengelola rumah sakit tidak mengurangi jumlah tempat tidur perawatan pasien dalam upaya memenuhi kriteria KRIS. "Pesan saya jangan dikurangi akses dengan mengurangi jumlah tempat tidur. Pertahankan jumlah tempat tidur dan penuhi persyaratannya dengan 12 kriteria tersebut," tegas Ghufron.
Penulis: Firman Hidranto Redaktur: Ratna Nuraini/Elvira Inda Sari Sumber: Indonesia.go.id
-
 @ f33c8a96:5ec6f741
2025-02-09 01:02:51
@ f33c8a96:5ec6f741
2025-02-09 01:02:51I have been working on account linking in the backend for a little while and so far only GitHub has been available to users (mostly for following the dev journey on the platform)
Now with this release the existing OAUTH options AND Nostr NIP-07 authentication are surfaced and able to be linked to an existing profile on your settings page.
Put simply this allows you to easily link email, GitHub, and nostr profile in the plebdevs platform to access the same account from different login methods. This will make it much easier to keep the same profile across multiple devices AND make sure that you never lose access!
Let me know what you think and PLEASE LET ME KNOW if you find any bugs! (I love bugs 🐛)
ONWARDS 🫡
originally posted at https://stacker.news/items/880161
-
 @ 266815e0:6cd408a5
2024-05-09 17:23:28
@ 266815e0:6cd408a5
2024-05-09 17:23:28Lot of people are starting to talk about building a web-of-trust and how nostr can or is already being used as such
We all know about using the kind:3 following lists as a simple WoT that can be used to filter out spam. but as we all know it does not really signal "trust", its mostly just "I find your content interesting"
But what about real "trust"... well its kind of multi-denominational, I could trust that your a good developer or a good journalist but still not trust you enough to invite you over to my house. There are some interesting and clever solutions proposed for quantifying "trust" in a digital sense but I'm not going to get into that here. I want to talk about something that I have not see anyone discuss yet.
How is the web-of-trust maintained? or more precisely how do you expect users to update the digital representation of the "trust" of other users?
Its all well and good to think of how a user would create that "trust" of another user when discovering them for the first time. They would click the "follow" button, or maybe even rate them on a few topics with a 1/5 star system But how will a user remove that trust? how will they update it if things change and they trust them less?
If our goal is to model "trust" in a digital sense then we NEED a way for the data to stay up-to-date and as accurate as possible. otherwise whats the use? If we don't have a friction-less way to update or remove the digital representation of "trust" then we will end up with a WoT that continuously grows and everyone is rated 10/10
In the case of nostr kind:3 following lists. its pretty easy to see how these would get updated. If someone posts something I dislike or I notice I'm getting board of their content. then I just unfollow them. An important part here is that I'm not thinking "I should update my trust score of this user" but instead "I'm no longer interested, I don't want to see this anymore"
But that is probably the easiest "trust" to update. because most of us on social media spend some time curating our feed and we are used to doing it. But what about the more obscure "trust" scores? whats the regular mechanism by which a user would update the "honestly" score of another user?
In the real world its easy, when I stop trusting someone I simply stop associating with them. there isn't any button or switch I need to update. I simply don't talk to them anymore, its friction-less But in the digital realm I would have to remove or update that trust. in other words its an action I need to take instead of an action I'm not doing. and actions take energy.
So how do we reflect something in the digital world that takes no-energy and is almost subconscious in the real world?
TLDR; webs-of-trust are not just about scoring other users once. you must keep the score up-to-date
-
 @ 266815e0:6cd408a5
2024-04-22 22:20:47
@ 266815e0:6cd408a5
2024-04-22 22:20:47While I was in Mediera with all the other awesome people at the first SEC cohort there where a lot of discussions around data storage on nostr and if it could be made censorship-resistent
I remember lots of discussions about torrents, hypercore, nostr relays, and of course IPFS
There were a few things I learned from all these conversations:
- All the existing solutions have one thing in common. A universal ID of some kind for files
- HTTP is still good. we don't have to throw the baby out with the bath water
- nostr could fix this... somehow
Some of the existing solutions work well for large files, and all of them are decentralization in some way. However none of them seem capable of serving up cat pictures for social media clients. they all have something missing...
An Identity system
An identity system would allow files to be "owned" by users. and once files have owners servers could start grouping files into a single thing instead of a 1000+ loose files
This can also greatly simplify the question of "what is spam" for a server hosting (or seeding) these files. since it could simply have a whitelist of owners (and maybe their friends)
What is blossom?
Blossom is a set of HTTP endpoints that allow nostr users to store and retrieve binary data on public servers using the sha256 hash as a universal id
What are Blobs?
blobs are chunks of binary data. they are similar to files but with one key difference, they don't have names
Instead blobs have a sha256 hash (like
b1674191a88ec5cdd733e4240a81803105dc412d6c6708d53ab94fc248f4f553) as an IDThese IDs are universal since they can be computed from the file itself using the sha256 hashing algorithm ( you can get a files sha256 hash on linux using:
sha256sum bitcoin.pdf)How do the servers work?
Blossom servers expose four endpoints to let clients and users upload and manage blobs
GET /<sha256>(optional file.ext)PUT /uploadAuthentication: Signed nostr event- Returns a blob descriptor
GET /list/<pubkey>- Returns an array of blob descriptors
Authentication(optional): Signed nostr eventDELETE /<sha256>Authentication: Signed nostr event
What is Blossom Drive?
Blossom Drive is a nostr app built on top of blossom servers and allows users to create and manage folders of blobs
What are Drives
Drives are just nostr events (kind
30563) that store a map of blobs and what filename they should have along with some extra metadataAn example drive event would be
json { "pubkey": "266815e0c9210dfa324c6cba3573b14bee49da4209a9456f9484e5106cd408a5", "created_at": 1710773987, "content": "", "kind": 30563, "tags": [ [ "name", "Emojis" ], [ "description", "nostr emojis" ], [ "d", "emojis" ], [ "r", "https://cdn.hzrd149.com/" ], [ "x", "303f018e613f29e3e43264529903b7c8c84debbd475f89368cb293ec23938981", "/noStrudel.png", "15161", "image/png" ], [ "x", "a0e2b39975c8da1702374b3eed6f4c6c7333e6ae0008dadafe93bd34bfb2ca78", "/satellite.png", "6853", "image/png" ], [ "x", "e8f3fae0f4a43a88eae235a8b79794d72e8f14b0e103a0fed1e073d8fb53d51f", "/amethyst.png", "20487", "image/png" ], [ "x", "70bd5836807b916d79e9c4e67e8b07e3e3b53f4acbb95c7521b11039a3c975c6", "/nos.png", "36521", "image/png" ], [ "x", "0fc304630279e0c5ab2da9c2769e3a3178c47b8609b447a30916244e89abbc52", "/primal.png", "29343", "image/png" ], [ "x", "9a03824a73d4af192d893329bbc04cd3798542ee87af15051aaf9376b74b25d4", "/coracle.png", "18300", "image/png" ], [ "x", "accdc0cdc048f4719bb5e1da4ff4c6ffc1a4dbb7cf3afbd19b86940c01111568", "/iris.png", "24070", "image/png" ], [ "x", "2e740f2514d6188e350d95cf4756bbf455d2f95e6a09bc64e94f5031bc4bba8f", "/damus.png", "32758", "image/png" ], [ "x", "2e019f08da0c75fb9c40d81947e511c8f0554763bffb6d23a7b9b8c9e8c84abb", "/old emojis/astral.png", "29365", "image/png" ], [ "x", "d97f842f2511ce0491fe0de208c6135b762f494a48da59926ce15acfdb6ac17e", "/other/rabbit.png", "19803", "image/png" ], [ "x", "72cb99b689b4cfe1a9fb6937f779f3f9c65094bf0e6ac72a8f8261efa96653f5", "/blossom.png", "4393", "image/png" ] ] }There is a lot going on but the main thing is the list of "x" tags and the path that describes the folder and filename the blob should live at
If your interested, the full event definition is at github.com/hzrd149/blossom-drive
Getting started
Like every good nostr client it takes a small instruction manual in order to use it properly. so here are the steps for getting started
1. Open the app
Open https://blossom.hzrd149.com
2. Login using extension

You can also login using any of the following methods using the input - NIP-46 with your https://nsec.app or https://flare.pub account - a NIP-46 connection string - an
ncryptsecpassword protected private key - ansecunprotected private key (please don't) - bunker:// URI from nsecbunker3. Add a blossom server

Right now
https://cdn.satellite.earthis the only public server that is compatible with blossom drive. If you want to host your own I've written a basic implementation in TypeScript github.com/hzrd149/blossom-server4. Start uploading your files
NOTE: All files upload to blossom drive are public by default. DO NOT upload private files

5. Manage files

Encrypted drives
There is also the option to encrypt drives using NIP-49 password encryption. although its not tested at all so don't trust it, verify

Whats next?
I don't know, but Im excited to see what everyone else on nostr builds with this. I'm only one developer at the end of the day and I can't think of everything
also all the images in this article are stored in one of my blossom drives here
nostr:naddr1qvzqqqrhvvpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qq8xzun5d93kcefdd9kkzem9wvr46jka
-
 @ d4309e24:8a81fcb0
2025-02-09 00:16:55
@ d4309e24:8a81fcb0
2025-02-09 00:16:551. What if You Could Send a Message into the Future?
Imagine leaving a message for your future self, a loved one, or even an entire community—one that no one, not even you, can unlock until a specific moment in time. Picture leaving a message for your children, a note of wisdom or love that remains hidden until they're old enough to appreciate it, all timed by Bitcoin's block height. You might also make a bold prediction about the future price of Bitcoin, sealing it away until the blockchain reaches a certain block height.
This is the idea behind Hatchstr, a decentralized app for time-locked messages that only unlock at predetermined Bitcoin block heights—no central authority required.
Why Build This?
I want to dive into the Nostr protocol not just by reading documentation, but by actually building something that embodies its core principles: censorship resistance, user ownership, and decentralization. Hatchstr is both an experiment and a contribution to the Nostr ecosystem—a way to test the limits of permissionless communication while learning and engaging with the community.
2. The Vision: How Hatchstr Would Work for Users
At its core, Hatchstr lets users create time capsules—encrypted messages that only become readable after a specified Bitcoin block height. Here’s what that looks like:
- You design a capsule with text and images using Hatchstr’s web app.
- You pick an unlock time (e.g., 1000 blocks from now).
- The message is encrypted, locked away, and published as a Nostr event.
- At the chosen time, the decryption key is revealed, allowing the recipient to finally access the message.

Potential Use Cases
-
Personal Messages: Send birthday wishes that unlock at midnight, time-delayed love letters, or notes to your future self.
-
Timed Learning: Lock educational content to unlock when students reach key learning stages or ages.
-
Creative Storytelling: Release serialized fiction, riddles, or treasure hunt clues that unlock over time.
-
Community & Events: Time-gate announcements for Nostr-based communities or scheduled voting mechanisms.
3. The Centralized Trap: Why Build on Nostr
When thinking about how to implement this, we could go the obvious, easy route:
- Store messages on a centralized server.
- Release them when the time is right.
- Let users download their messages.
Simple, right? But is it the right approach? Let's break it down.
Why This Fails
-
Single Point of Failure: If my server goes down, all messages are unavailable.
-
Privacy Risks: Users would need to trust me not to access their messages.
-
Ownership & Longevity: What happens if I lose interest? The system dies with me.

A centralized model defeats the purpose of time-locking messages. Users shouldn’t have to trust a third party. We need decentralization.
4. Nostr to the Rescue: How Decentralization Can Help
Instead of a single server holding messages hostage, Nostr allows users to publish messages to decentralized relays. Here are the key differences:
-
Nostr IDs = Self-Owned Identities: Your public key is your identity, not tied to any company.
-
Relays = Decentralized Bulletin Boards: Anyone can run one, ensuring redundancy and censorship resistance.
-
Messages = Signed Events: Cryptographically signed by the sender or encrypted for only the recipient.

How Nostr Reduces Centralization
In this version of Hatchstr, capsules are still stored in a centralized manner at first until they 'hatch'. However, once the Bitcoin block height condition is met:
- Capsule Publication: The system publishes the capsule events to Nostr relays, making the messages available for decryption by the intended recipients.
This approach, while not eliminating the central server, allows for:
-
Third-Party Clients: Developers can now create clients that interact with Hatchstr capsules on Nostr, enhancing the system's openness and potentially leading to a richer ecosystem around time-locked messages.
-
Decentralized Access: Even though the initial storage is centralized, the access to the messages becomes decentralized once published to Nostr, reducing the dependency on a single point for message retrieval.
We have some improvements, but I am sure we can do better!
5. The Path to Decentralized Timekeeping
The Timeless Nature of Encryption
Encrypted messages exist outside time—once locked, they remain secure indefinitely. Modern cryptography (like AES-256) doesn’t "expire" or weaken unless decrypted (excluding brute force attacks). This creates a paradox: How do you bind something timeless to a specific moment in the physical world?
The Time-Lock Puzzle Dilemma
Cryptographers have proposed time-lock puzzles—encryption that requires sustained computation to unlock, theoretically forcing a minimum wait time. But these face critical hurdles:
-
Hardware Uncertainty
Solving time depends on an attacker’s computational power. A nation-state could crack in hours what takes years for a regular user. -
No Real-World Alignment
Puzzles can’t guarantee unlocks align with calendar dates or real-world events ("unlock on my child’s 18th birthday"). -
Energy Waste
Requires continuous computation, making it environmentally impractical for longer time locking.
Bitcoin as a Decentralized Clock
This is where Bitcoin’s blockchain shines. Its difficulty-adjusted proof-of-work acts as a trustless metronome:
-
Predictable Rhythm
Despite hash rate fluctuations, the 10-minute block target (via difficulty adjustments) creates a consistent approximation of real-world time.
-
Immutable History
Block height 1,000,000 will always correspond to the same point in Bitcoin’s timeline, regardless of future changes in mining power
Splitting the Problem
Hatchstr can bridge timeless encryption and blockchain timing by separating concerns:
1. Capsules – The time-locked message itself:
-
Design independent of the time-locking mechanism.
-
Encrypted client-side.
-
Content stored anywhere the user wants (IPFS, personal servers, etc.).
-
Completely owned by the user—not Hatchstr.
2. Clock Servers – Independent, lightweight timing nodes that:
-
Only publish decryption keys when the target Bitcoin block height is reached.
-
Users can choose which Clock Server to trust.
-
Anyone can run their own Clock Server.
-
Multiple servers can coordinate to prevent a single point of failure.

This means Hatchstr itself doesn’t store anything—users are fully in control.
6. What Comes Next
This project is just beginning—a blueprint with open questions and untested assumptions. In the next two articles, I’ll explore how to turn this concept into something tangible. First, how we might design playful time capsules that can be displayed faithfully by multiple clients, balancing creativity with decentralization. Then, the messy realities of clock servers: why federating them matters, how to incentivize reliability, and borrow Bitcoin’s rhythm without centralizing control. We will dive into setting up a simple clock server to get things started.
I’m still learning Nostr’s ecosystem, and this project is as much about sharing my education as anything else. If any part of this concept makes you think “yes, but…” or “what if…”, I’d genuinely love to hear it. Find me on Nostr – no expertise required, just an interest in sending messages to the future. :

npub16scfufrpsqcukjg7ymu4r40h7j4dwqy4pajgz48e6lmnmz5pljcqh678uhThank you for reading 🧡
-
 @ f977c464:32fcbe00
2024-01-30 20:06:18
@ f977c464:32fcbe00
2024-01-30 20:06:18Güneşin kaybolmasının üçüncü günü, saat öğlen on ikiyi yirmi geçiyordu. Trenin kalkmasına yaklaşık iki saat vardı. Hepimiz perondaydık. Valizlerimiz, kolilerimiz, renk renk ve biçimsiz çantalarımızla yan yana dizilmiş, kısa aralıklarla tepemizdeki devasa saati kontrol ediyorduk.
Ama ne kadar dik bakarsak bakalım zaman bir türlü istediğimiz hızla ilerlemiyordu. Herkes birkaç dakika sürmesi gereken alelade bir doğa olayına sıkışıp kalmış, karanlıktan sürünerek çıkmayı deniyordu.
Bekleme salonuna doğru döndüm. Nefesimden çıkan buharın arkasında, kalın taş duvarları ve camlarıyla morg kadar güvenli ve soğuk duruyordu. Cesetleri o yüzden bunun gibi yerlere taşımaya başlamışlardı. Demek insanların bütün iyiliği başkaları onları gördüğü içindi ki gündüzleri gecelerden daha karanlık olduğunda hemen birbirlerinin gırtlağına çökmüş, böğürlerinde delikler açmış, gözlerini oyup kafataslarını parçalamışlardı.
İstasyonun ışığı titrediğinde karanlığın enseme saplandığını hissettim. Eğer şimdi, böyle kalabalık bir yerde elektrik kesilse başımıza ne gelirdi?
İçerideki askerlerden biri bakışlarımı yakalayınca yeniden saate odaklanmış gibi yaptım. Sadece birkaç dakika geçmişti.
“Tarlalarım gitti. Böyle boyum kadar ayçiçeği doluydu. Ah, hepsi ölüp gidiyor. Afitap’ın çiçekleri de gi-”
“Dayı, Allah’ını seversen sus. Hepimizi yakacaksın şimdi.”
Karanlıkta durduğunda, görünmez olmayı istemeye başlıyordun. Kimse seni görmemeli, nefesini bile duymamalıydı. Kimsenin de ayağının altında dolaşmamalıydın; gelip kazayla sana çarpmamalılar, takılıp sendelememeliydiler. Yoksa aslında hedefi sen olmadığın bir öfke gürlemeye başlar, yaşadığın ilk şoku ve acıyı silerek üstünden geçerdi.
İlk konuşan, yaşlıca bir adam, kafasında kasketi, nasırlı ellerine hohluyordu. Gözleri ve burnu kızarmıştı. Güneşin kaybolması onun için kendi başına bir felaket değildi. Hayatına olan pratik yansımalarından korkuyordu olsa olsa. Bir anının kaybolması, bu yüzden çoktan kaybettiği birinin biraz daha eksilmesi. Hayatta kalmasını gerektiren sebepler azalırken, hayatta kalmasını sağlayacak kaynaklarını da kaybediyordu.
Onu susturan delikanlıysa atkısını bütün kafasına sarmış, sakalı ve yüzünün derinliklerine kaçmış gözleri dışında bedeninin bütün parçalarını gizlemeye çalışıyordu. İşte o, güneşin kaybolmasının tam olarak ne anlama geldiğini anlamamış olsa bile, dehşetini olduğu gibi hissedebilenlerdendi.
Güneşin onlardan alındıktan sonra kime verileceğini sormuyorlardı. En başta onlara verildiğinde de hiçbir soru sormamışlardı zaten.
İki saat ne zaman geçer?
Midemin üstünde, sağ tarafıma doğru keskin bir acı hissettim. Karaciğerim. Gözlerimi yumdum. Yanımda biri metal bir nesneyi yere bıraktı. Bir kafesti. İçerisindeki kartalın ıslak kokusu burnuma ulaşmadan önce bile biliyordum bunu.
“Yeniden mi?” diye sordu bana kartal. Kanatları kanlı. Zamanın her bir parçası tüylerinin üstüne çöreklenmişti. Gagası bir şey, tahminen et parçası geveliyor gibi hareket ediyordu. Eski anılar kolay unutulmazmış. Şu anda kafesinin kalın parmaklıklarının ardında olsa da bunun bir aldatmaca olduğunu bir tek ben biliyordum. Her an kanatlarını iki yana uzatıverebilir, hava bu hareketiyle dalgalanarak kafesi esneterek hepimizi içine alacak kadar genişleyebilir, parmaklıklar önce ayaklarımızın altına serilir gibi gözükebilir ama aslında hepimizin üstünde yükselerek tepemize çökebilirdi.
Aşağıya baktım. Tahtalarla zapt edilmiş, hiçbir yere gidemeyen ama her yere uzanan tren rayları. Atlayıp koşsam… Çantam çok ağırdı. Daha birkaç adım atamadan, kartal, suratını bedenime gömerdi.
“Bu sefer farklı,” diye yanıtladım onu. “Yeniden diyemezsin. Tekrarladığım bir şey değil bu. Hatta bir hata yapıyormuşum gibi tonlayamazsın da. Bu sefer, insanların hak etmediğini biliyorum.”
“O zaman daha vahim. Süzme salaksın demektir.”
“İnsanların hak etmemesi, insanlığın hak etmediği anlamına gelmez ki.”
Az önce göz göze geldiğim genççe ama çökük asker hâlâ bana bakıyordu. Bir kartalla konuştuğumu anlamamıştı şüphesiz. Yanımdakilerden biriyle konuştuğumu sanmış olmalıydı. Ama konuştuğum kişiye bakmıyordum ona göre. Çekingence kafamı eğmiştim. Bir kez daha göz göze geldiğimizde içerideki diğer iki askere bir şeyler söyledi, onlar dönüp beni süzerken dışarı çıktı.
Yanımızdaki, az önce konuşan iki adam da şaşkınlıkla bir bana bir kartala bakıyordu.
“Yalnız bu sefer kalbin de kırılacak, Prometheus,” dedi kartal, bana. “Belki son olur. Biliyorsun, bir sürü soruna neden oluyor bu yaptıkların.”
Beni koruyordu sözde. En çok kanıma dokunan buydu. Kasıklarımın üstüne oturmuş, kanlı suratının ardında gözleri parlarken attığı çığlık kulaklarımda titremeye devam ediyordu. Bu tabloda kimsenin kimseyi düşündüğü yoktu. Kartalın, yanımızdaki adamların, artık arkama kadar gelmiş olması gereken askerin, tren raylarının, geçmeyen saatlerin…
Arkamı döndüğümde, asker sahiden oradaydı. Zaten öyle olması gerekiyordu; görmüştüm bunu, biliyordum. Kehanetler… Bir şeyler söylüyordu ama ağzı oynarken sesi çıkmıyordu. Yavaşlamış, kendisini saatin akışına uydurmuştu. Havada donan tükürüğünden anlaşılıyordu, sinirliydi. Korktuğu için olduğunu biliyordum. Her seferinde korkmuşlardı. Beni unutmuş olmaları işlerini kolaylaştırmıyordu. Sadece yeni bir isim vermelerine neden oluyordu. Bu seferkiyle beni lanetleyecekleri kesinleşmişti.
Olması gerekenle olanların farklı olması ne kadar acınasıydı. Olması gerekenlerin doğasının kötücül olmasıysa bir yerde buna dayanıyordu.
“Salaksın,” dedi kartal bana. Zamanı aşan bir çığlık. Hepimizin önüne geçmişti ama kimseyi durduramıyordu.
Sonsuzluğa kaç tane iki saat sıkıştırabilirsiniz?
Ben bir tane bile sıkıştıramadım.
Çantama uzanıyordum. Asker de sırtındaki tüfeğini indiriyordu. Benim acelem yoktu, onunsa eli ayağı birbirine dolaşıyordu. Oysaki her şey tam olması gerektiği anda olacaktı. Kehanet başkasının parmaklarının ucundaydı.
Güneş, bir tüfeğin patlamasıyla yeryüzüne doğdu.
Rayların üzerine serilmiş göğsümün ortasından, bir çantanın içinden.
Not: Bu öykü ilk olarak 2021 yılında Esrarengiz Hikâyeler'de yayımlanmıştır.
-
 @ 16d11430:61640947
2025-02-09 00:12:22
@ 16d11430:61640947
2025-02-09 00:12:22Introduction: The Power of Focused Attention
In an age of distraction, power is not merely held through material wealth, authority, or control over others—it is built through focused attention. The human brain, a complex quantum-biological processor, constructs reality through perception. When harnessed correctly, focused attention allows individuals to transcend limitations, reshape their reality, and live free.
Power, then, is not external—it is a construct supported by the mind and created within the brain. Understanding how this works offers a path to transcendence, autonomy, and liberation from imposed limitations.
The Neuroscience of Focused Attention: Constructing Reality
The brain is a prediction engine, constantly processing information and filtering out irrelevant stimuli. Focused attention directs this process, acting as a spotlight that selects what becomes part of one's conscious experience. This is the fundamental mechanism behind cognitive power.
- Neuroplasticity: Building Power Through Repetition
The brain adapts to repeated stimuli through neuroplasticity. What one focuses on consistently rewires neural pathways, strengthening certain thoughts, beliefs, and abilities. Over time, this focus builds an internal structure of power—a network of ideas and perceptions that define one’s reality.
If one focuses on problems, they grow.
If one focuses on solutions, they appear.
If one focuses on fear, it shapes perception.
If one focuses on mastery, skills develop.
- The Quantum Mind: Attention as a Creative Force
Quantum physics suggests that observation influences reality. Just as subatomic particles behave differently when measured, focused attention may act as a force that shapes possibilities into tangible outcomes.
This aligns with the ancient concept that "energy flows where attention goes." What one attends to with intention can manifest as action, opportunity, and ultimately, freedom.
- The Reticular Activating System (RAS): Filtering Reality
The Reticular Activating System (RAS) in the brainstem acts as a gatekeeper for focus. It determines what information enters conscious awareness. When trained, it can filter out distractions and amplify pathways toward a desired goal.
Want to see opportunities? Program the RAS by setting clear intentions.
Want to break free from limiting beliefs? Train focus away from conditioned fears.
The Mind’s Role: Transcending Limitations
The mind is the interpreter of the brain’s electrical and biochemical activity. While the brain processes raw data, the mind provides meaning. This distinction is crucial because meaning determines how one experiences reality.
- Breaking Mental Chains: Rewriting Narratives
Most limitations are narratives—stories imposed by culture, society, or personal history. True power lies in rewriting these stories.
Instead of “I am trapped by my circumstances,” shift to “I create my own reality.”
Instead of “I need permission,” shift to “I give myself permission.”
By restructuring meaning, the mind can redefine the limits of what is possible.
- The Silence Paradox: Accessing Higher States
Silence, both literal and mental, creates space for higher-order thinking. Just as quantum tunneling allows subatomic particles to pass through barriers without energy loss, silence allows the mind to bypass noise and access deeper intelligence.
Meditation, stillness, and solitude amplify internal power.
The ability to not react is a form of control over external influence.
True mastery comes from detachment—engaging the world without being controlled by it.
Transcendence: Living Free Through Mental Autonomy
To transcend means to rise above imposed structures—whether societal, psychological, or energetic. The construct of power built through focused attention allows one to escape control mechanisms and live autonomously.
- Sovereignty of Mind: Owning One’s Thoughts
A free mind is one that chooses its inputs rather than being programmed by external forces. This requires:
Awareness of mental conditioning (social narratives, propaganda, biases)
Intentional thought selection (curating what enters the mental space)
Guarding attention fiercely (not allowing distraction to hijack focus)
- Detachment From Control Structures
Society operates on the principle of attention capture—through media, politics, and algorithms that direct thought patterns. Escaping these requires detachment.
Do not react emotionally to fear-based programming.
Cultivate independent thought by questioning imposed narratives.
Reduce external noise to amplify internal wisdom.
- The Flow State: Moving Beyond Constraints
When focus is refined to its highest degree, one enters flow state—a condition where action and awareness merge, and limitations dissolve.
In flow, work becomes effortless.
Creativity becomes boundless.
Freedom becomes not just a philosophy, but a lived experience.
Conclusion: The Mind as the Ultimate Key to Freedom
Power is not an external possession—it is the ability to direct one’s own focus. Through the interplay of brain function, cognitive attention, and mental discipline, one constructs personal sovereignty. The individual who masters focus, controls reality.
Freedom is not given. It is built—through attention, intention, and an unwavering commitment to mental autonomy.
-
 @ 16d11430:61640947
2025-02-08 23:54:40
@ 16d11430:61640947
2025-02-08 23:54:40Language is more than just words—it’s a pattern, a rhythm, a system of meaning that our brains decode in different ways. While most people learn language analytically, breaking it down into individual words and sentences, gestalt language processors (GLP) acquire language in a completely different way. They learn in chunks, grasping entire phrases and only later dissecting them into smaller parts.
This unique method of language acquisition is often observed in autistic individuals and those with alternative cognitive processing styles. But what happens when such a learner interacts with a highly inflected, agglutinative language like Malayalam? As it turns out, Malayalam might be one of the best-suited languages for gestalt language processors, thanks to its natural structure, flexible syntax, and phrase-based meaning.
Let’s explore why Malayalam aligns so well with gestalt processing and how it compares to other languages.
Understanding Gestalt Language Processing
Gestalt language processing is the ability to acquire and use language in whole phrases rather than as individual words. Instead of learning word-by-word, GLP learners store entire sentences or expressions they hear and later modify them into new, meaningful statements.
For example, a child who is a gestalt processor might initially say: ➡ "Do you want some juice?" (because they've heard it as a whole phrase) Later, they might extract parts and start saying: ➡ "Want juice." Finally, they construct their own original sentence: ➡ "I want juice."
This approach is pattern-based rather than rule-based, making Malayalam an excellent match due to its agglutinative grammar, rhythmic structure, and flexible word order.
How Malayalam Supports Gestalt Language Processing
- Malayalam’s Agglutinative Nature Encourages Chunk Learning
Malayalam, like other Dravidian languages, is highly agglutinative, meaning words are built using multiple suffixes that change meaning. Instead of discrete words, many phrases function as a single semantic unit—which is exactly how GLP learners process language.
Take the word "വീട്" (vīṭu) meaning "house":
വീട്ടിൽ (vīṭṭil) – in the house
വീട്ടിലേക്ക് (vīṭṭilēkk) – towards the house
വീട്ടിലേക്കു പോകുന്നു (vīṭṭilēkku pōkunnu) – going to the house
A gestalt processor might first acquire "വീട്ടിലേക്കു പോകുന്നു" as a chunk, rather than breaking it into individual words. Over time, they start recognizing patterns and modifying them.
This is in contrast to English, where "going" and "house" are learned separately before forming a phrase like "going to the house."
- Flexible Word Order Aligns with Pattern-Based Learning
Malayalam allows word order variations without losing meaning, making it an intuitive fit for gestalt learners who focus on meaning first rather than strict syntax.
For example, the sentence "I drank tea" can be expressed in multiple ways in Malayalam:
ഞാൻ ചായ കുടിച്ചു. (ñān cāya kuṭiccu) – Standard word order
ചായ ഞാൻ കുടിച്ചു. (cāya ñān kuṭiccu) – Emphasizing "tea"
കുടിച്ചു ഞാൻ ചായ. (kuṭiccu ñān cāya) – Focus on the action
A gestalt learner might acquire an entire phrase like "ചായ കുടിക്കണോ?" ("Do you want tea?") and later extract the verb "കുടി" (drink) or the noun "ചായ" (tea) as they develop more flexible speech.
In contrast, languages like English and French have more rigid word order, making it harder for gestalt learners to generalize.
- Long and Embedded Sentence Structures Favor Chunk-Based Processing
Malayalam commonly uses long, nested sentences, which gestalt learners store as full units before breaking them down.
For example:
അവൻ പറഞ്ഞത് ഞാൻ അറിഞ്ഞില്ല. (avan paṟaññatu ñān aṟiññilla)
Literal: "What he said, I didn’t know."
Gestalt learners may first acquire: "അവൻ പറഞ്ഞത്" ("What he said") as a single unit before extracting "പറഞ്ഞത്" (said).
This mirrors how **gestalt processors extract meaning from larger linguistic units over time.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28O Planetinha
Fumaça verde me entrando pelas narinas e um coro desafinado fazia uma base melódica.
nos confins da galáxia havia um planetinha isolado. Era um planeta feliz.
O homem vestido de mago começava a aparecer por detrás da fumaça verde.
O planetinha recebeu três presentes, mas o seu habitante, o homem, estava num estado de confusão tão grande que ameaçava estragá-los. Os homens já havia escravizado o primeiro presente, a vida; lutavam contra o segundo presente, a morte; e havia alguns que achavam que deviam destruir totalmente o terceiro, o amor, e com isto levar a desordem total ao pobre planetinha perdido, que se chamava Terra.
O coro desafinado entrou antes do "Terra" cantando várias vezes, como se imitasse um eco, "terra-terra-terraaa". Depois de uma pausa dramática, o homem vestido de mago voltou a falar.
Terra, nossa nave mãe.
Neste momento eu me afastei. À frente do palco onde o mago e seu coral faziam apelos à multidão havia vários estandes cobertos com a tradicional armação de quatro pernas e lona branca. Em todos os cantos da praça havia gente, gente dos mais variados tipos. Visitantes curiosos que se aproximavam atraídos pela fumaça verde e as barraquinhas, gente que aproveitava o movimento para vender doces sem pagar imposto, casais que se abraçavam de pé para espantar o frio, os tradicionais corredores que faziam seu cooper, gente cheia de barba e vestida para imitar os hippies dos anos 60 e vender colares estendidos no chão, transeuntes novos e velhos, vestidos como baladeiros ou como ativistas do ônibus grátis, grupos de ciclistas entusiastas.
O mago fazia agora apelos para que nós, os homens, habitantes do isolado planetinha, passássemos a ver o planetinha, nossa nave mãe, como um todo, e adquiríssemos a consciência de que ele estava entrando em maus lençóis. A idéia, reforçada pela logomarca do evento, era que parássemos de olhar só para a nossa vida e pensássemos no planeta.
A logomarca do evento, um desenho estilizado do planeta Terra, nada tinha a ver com seu nome: "Festival Andando de Bem com a Vida", mas havia sido ali colocada estrategicamente pelos organizadores, de quem parecia justamente sair a mensagem dita pelo mago.
Aquela multidão de pessoas que, assim como eu, tinham suas próprias preocupações, não podiam ver o quadro caótico que formavam, cada uma com seus atos isolados, ali naquela praça isolada, naquele planeta isolado. Quando o hippie barbudo, quase um Osho, assustava um casal para tentar vender-lhes um colar, a quantidade de caos que isto acrescentava à cena era gigantesca. Por um segundo, pude ver, como se estivesse de longe e acima, com toda a pretensão que este estado imaginativo carrega, a cena completa do caos.
Uma nave-mãe, dessas de ficção científica, habitada por milhões de pessoas, seguia no espaço sem rumo, e sem saber que logo à frente um longo precipício espacial a esperava, para a desgraça completa sua e de seus habitantes.
Acostumados àquela nave tanto quanto outrora estiveram acostumados à sua terra natal, os homens viviam as próprias vidas sem nem se lembrar que estavam vagando pelo espaço. Ninguém sabia quem estava conduzindo a nave, e ninguém se importava.
No final do filme descobre-se que era a soma completa do caos que cada habitante produzia, com seus gestos egoístas e incapazes de levar em conta a totalidade, é que determinava a direção da nave-mãe. O efeito, no entanto, não era imediato, como nunca é. Havia gente de verdade encarregada de conduzir a nave, mas era uma gente bêbada, mau-caráter, que vivia brigando pelo controle da nave e o poder que isto lhes dava. Poder, status, dinheiro!
Essa gente bêbada era atraída até ali pela corrupção das instituições e da moral comum que, no fundo no fundo, era causada pelo egoísmo da população, através de um complexo -- mas que no filme aparece simplificado pela ação individual de um magnata do divertimento público -- processo social.
O homem vestido de mago era mais um agente causador de caos, com sua cena cheia de fumaça e sua roupa estroboscópica, ele achava que estava fazendo o bem ao alertar sua platéia, todos as sextas-feiras, de que havia algo que precisava ser feito, que cada um que estava ali ouvindo era responsável pelo planeta. A sua incapacidade, porém, de explicar o que precisava ser feito só aumentava a angústia geral; a culpa que ele jogava sobre seu público, e que era prontamente aceita e passada em frente, aos familiares e amigos de cada um, atormentava-os diariamente e os impedia de ter uma vida decente no trabalho e em casa. As famílias, estressadas, estavam constantemente brigando e os motivos mais insignificantes eram responsáveis pelas mais horrendas conseqüências.
O mago, que após o show tirava o chapéu entortado e ia tomar cerveja num boteco, era responsável por uma parcela considerável do caos que levava a nave na direção do seu desgraçado fim. No filme, porém, um dos transeuntes que de passagem ouviu um pedaço do discurso do mago despertou em si mesmo uma consiência transformadora e, com poderes sobre-humanos que lhe foram então concedidos por uma ordem iniciática do bem ou não, usando só os seus poderes humanos mesmo, o transeunte -- na primeira versão do filme um homem, na segunda uma mulher -- consegue consertar as instituições e retirar os bêbados da condução da máquina. A questão da moral pública é ignorada para abreviar a trama, já com duas horas e quarenta de duração, mas subentende-se que ela também fora resolvida.
No planeta Terra real, que não está indo em direção alguma, preso pela gravidade ao Sol, e onde as pessoas vivem a própria vida porque lhes é impossível viver a dos outros, não têm uma consciência global de nada porque só é possível mesmo ter a consciência delas mesmas, e onde a maioria, de uma maneira ou de outra, está tentando como pode, fazer as coisas direito, o filme é exibido.
Para a maioria dos espectadores, é um filme que evoca reflexões, um filme forte. Por um segundo elas têm o mesmo vislumbre do caos generalizado que eu tive ali naquela praça. Para uma pequena parcela dos espectadores -- entre eles alguns dos que estavam na platéia do mago, o próprio mago, o seguidor do Osho, o casal de duas mulheres e o vendedor de brigadeiros, mas aos quais se somam também críticos de televisão e jornal e gente que fala pelos cotovelos na internet -- o filme é um horror, o filme é uma vulgarização de um problema real e sério, o filme apela para a figura do herói salvador e passa uma mensagem totalmente errada, de que a maioria da população pode continuar vivendo as suas própria vidinhas miseráveis enquanto espera por um herói que vem do Olimpo e os salva da mixórdia que eles mesmos causaram, é um filme que presta um enorme desserviço à causa.
No dia seguinte ao lançamento, num bar meio caro ali perto da praça, numa mesa com oito pessoas, entre elas seis do primeiro grupo e oito do segundo, discute-se se o filme levará ou não o Oscar. Eu estou em casa dormindo e não escuto nada.
-
 @ 16d11430:61640947
2025-02-08 23:31:00
@ 16d11430:61640947
2025-02-08 23:31:00A Hitchhiker’s Guide to Intergalactic Trade, Verified on the Blockchain
Somewhere in the unfashionable backwaters of the Milky Way, a small blue planet is busy debating whether it should be more concerned about social media algorithms or the growing irrelevance of its own economy. Meanwhile, out there in the cosmic gigaverse, civilizations with far more interesting problems are engaging in the great intergalactic hustle—trading tech, swapping energy signatures, and making quantum side deals faster than you can say "proof-of-work."
Humanity, as per usual, has arrived late to the party but is hoping to slip in unnoticed and pretend like it’s been part of the game all along. The problem? We don’t know the rules, we don’t know what we have to offer, and most importantly, we don’t even have an invite.
Fortunately, the universe is a decentralized, peer-to-peer system, much like Bitcoin—only with fewer arguments on Twitter. And if we play this right, we might just hustle our way into the Universal Indira Net, the cosmic marketplace where civilizations exchange technology, knowledge, and, quite possibly, dad jokes that transcend space-time.
Step 1: Plugging into the Universal Indira Net
According to ancient Hindu mythology, Indra’s Net is an infinite web where each node reflects all others, meaning everything is connected to everything else, forever. Sounds poetic, right? Well, take that concept, throw in some decentralized cryptographic verification, and you've got the backbone of a cosmic trade network where trust isn’t just assumed—it’s mathematically proven.
In theory, Earth should be able to sync up with the Universal Indira Net, but there’s one small problem: our civilization hasn’t even solved its own internet yet. Forget interstellar trade—we still struggle with buffering. Until we build long-range, high-bandwidth, interference-proof communication systems, we’re basically screaming into the void, hoping someone hears us (and doesn’t immediately categorize us as "primitive and likely to start wars over fictional borders").
Luckily, we are making some progress:
NASA’s Laser-Based Comms: Just last year, NASA’s Deep Space Optical Communications (DSOC) project sent data 19 million miles at broadband speeds. In galactic terms, this is the equivalent of tossing a USB drive across your front yard, but hey, it’s a start. (source)
Quantum Entanglement Messaging: Scientists are theorizing about using spooky action at a distance to send information instantaneously across the galaxy. Of course, it’s still at the “we swear this works on paper” stage.
Gravitational Wave Emails: There’s a wild theory that gravitational waves could be harnessed for communication, which means the universe has literally been shaking with missed calls for billions of years.
If we can bootstrap any of these into a reliable cosmic broadband, we might just be able to negotiate our way into the interstellar group chat.
Step 2: What Do We Bring to the Table?
Now, assuming we finally manage to stop talking to ourselves and make first contact, the next big question is: what the hell do we trade?
Here’s what we know about intergalactic economics:
-
No one wants our money – Fiat currency is an Earth-only meme. The only currency that might hold value out there is Bitcoin, because at least it’s energy-backed and provably scarce. But even then, aliens are likely using something far more advanced—probably a universal ledger that encodes information directly into quantum spacetime fabric.
-
Physical goods are inefficient – Nobody’s going to fly across light-years to pick up a shipment of human-made Teslas when they can 3D print their own antimatter-powered space yacht.
-
Knowledge is king – The real hustle is in information. Code, algorithms, AI models—things that can be transmitted at the speed of light and verifiably proven on-chain.
Trade Goods That Might Actually Be Worth Something:
AI & Quantum Computing Models – If we develop AI that thinks in ways alien civilizations haven’t considered, we’ve got intellectual property worth trading.
Biological Engineering & Longevity Tech – If Earth figures out how to stop aging, you can bet intergalactic billionaires (assuming they exist) would pay for that.
Mathematical Breakthroughs – Math is the universal language, and if we crack new fundamental theorems, we might just have something of value.
Which means the best way to hustle our way into the Indira Net is to become the best at something. And right now, the only thing we’ve truly mastered is making memes and overcomplicating financial systems.
Step 3: Navigating the Cosmic Trade Rules
Of course, even if we have something valuable, trading with advanced civilizations isn’t as simple as sending an invoice.
We don’t even know the rules of interstellar engagement yet. But if galactic trade works anything like human history, we should expect:
Regulatory Compliance – Because even in space, there’s bound to be paperwork. If we get lucky, aliens might use smart contracts instead of lawyers.
Sanctions & Trade Embargoes – You think Earth’s geopolitics are complicated? Try interstellar diplomacy, where embargoes might involve entire planetary quarantines.
Intellectual Property Theft – If we’re not careful, we might trade away humanity’s most valuable discovery for an alien NFT that depreciates instantly.
Which is why any trade network must be built on provable, immutable verification systems—aka, blockchain.
This is where DamageBDD, Bitcoin, and cryptographic proofs come into play. If we can create a system that ensures:
✅ Technology is verified before it’s traded ✅ Ownership and utility are recorded on an immutable ledger ✅ Contracts execute autonomously with zero-trust mechanics
Then we might just stand a chance of becoming a respected node in the Universal Indira Net, rather than a civilization that gets rug-pulled by intergalactic venture capitalists.
Final Thought: The Cosmic Hustle is Just Beginning
Humanity is still in the tutorial level of the interstellar economy. We’re fumbling with our first trade attempts, trying not to get exploited, and desperately figuring out how not to be the cosmic equivalent of a developing nation selling raw materials to advanced intergalactic conglomerates.
But if we:
Build high-speed interstellar comms
Develop technology that is uniquely valuable
Create trustless, verifiable trade systems
…then we won’t just be another planetary backwater. We’ll be a node in the greatest decentralized network of all time.
The Cosmic Hustle is real. The only question is: will we be the hustlers or the ones getting hustled?
-
-
 @ f977c464:32fcbe00
2024-01-11 18:47:47
@ f977c464:32fcbe00
2024-01-11 18:47:47Kendisini aynada ilk defa gördüğü o gün, diğerleri gibi olduğunu anlamıştı. Oysaki her insan biricik olmalıydı. Sözgelimi sinirlendiğinde bir kaşı diğerinden birkaç milimetre daha az çatılabilirdi veya sevindiğinde dudağı ona has bir açıyla dalgalanabilirdi. Hatta bunların hiçbiri mümkün değilse, en azından, gözlerinin içinde sadece onun sahip olabileceği bir ışık parlayabilirdi. Çok sıradan, öyle sıradan ki kimsenin fark etmediği o milyonlarca minik şeyden herhangi biri. Ne olursa.
Ama yansımasına bakarken bunların hiçbirini bulamadı ve diğer günlerden hiç de farklı başlamamış o gün, işe gitmek için vagonunun gelmesini beklediği alelade bir metro istasyonunda, içinde kaybolduğu illüzyon dağılmaya başladı.
İlk önce derisi döküldü. Tam olarak dökülmedi aslında, daha çok kıvılcımlara dönüşüp bedeninden fırlamış ve bir an sonra sönerek külleşmiş, havada dağılmıştı. Ardında da, kaybolmadan hemen önce, kısa süre için hayal meyal görülebilen, bir ruhun yok oluşuna ağıt yakan rengârenk peri cesetleri bırakmıştı. Beklenenin aksine, havaya toz kokusu yayıldı.
Dehşete düştü elbette. Dehşete düştüler. Panikle üstlerini yırtan 50 işçi. Her şeyin sebebiyse o vagon.
Saçları da döküldü. Her tel, yere varmadan önce, her santimde ikiye ayrıla ayrıla yok oldu.
Bütün yüzeylerin mat olduğu, hiçbir şeyin yansımadığı, suyun siyah aktığı ve kendine ancak kameralarla bakabildiğin bir dünyada, vagonun içine yerleştirilmiş bir aynadan ilk defa kendini görmek.
Gözlerinin akları buharlaşıp havada dağıldı, mercekleri boşalan yeri doldurmak için eriyip yayıldı. Gerçeği görmemek için yaratılmış, bu yüzden görmeye hazır olmayan ve hiç olmayacak gözler.
Her şeyin o anda sona erdiğini sanabilirdi insan. Derin bir karanlık ve ölüm. Görmenin görmek olduğu o anın bitişi.
Ben geldiğimde ölmüşlerdi.
Yani bozulmuşlardı demek istiyorum.
Belleklerini yeni taşıyıcılara takmam mümkün olmadı. Fiziksel olarak kusursuz durumdaydılar, olmayanları da tamir edebilirdim ama tüm o hengamede kendilerini baştan programlamış ve girdilerini modifiye etmişlerdi.
Belleklerden birini masanın üzerinden ileriye savurdu. Hınca hınç dolu bir barda oturuyorlardı. O ve arkadaşı.
Sırf şu kendisini insan sanan androidler travma geçirip delirmesin diye neler yapıyoruz, insanın aklı almıyor.
Eliyle arkasını işaret etti.
Polislerin söylediğine göre biri vagonun içerisine ayna yerleştirmiş. Bu zavallılar da kapı açılıp bir anda yansımalarını görünce kafayı kırmışlar.
Arkadaşı bunların ona ne hissettirdiğini sordu. Yani o kadar bozuk, insan olduğunu sanan androidi kendilerini parçalamış olarak yerde görmek onu sarsmamış mıydı?
Hayır, sonuçta belirli bir amaç için yaratılmış şeyler onlar. Kaliteli bir bilgisayarım bozulduğunda üzülürüm çünkü parasını ben vermişimdir. Bunlarsa devletin. Bana ne ki?
Arkadaşı anlayışla kafasını sallayıp suyundan bir yudum aldı. Kravatını biraz gevşetti.
Bira istemediğinden emin misin?
İstemediğini söyledi. Sahi, neden deliriyordu bu androidler?
Basit. Onların yapay zekâlarını kodlarken bir şeyler yazıyorlar. Yazılımcılar. Biliyorsun, ben donanımdayım. Bunlar da kendilerini insan sanıyorlar. Tiplerine bak.
Sesini alçalttı.
Arabalarda kaza testi yapılan mankenlere benziyor hepsi. Ağızları burunları bile yok ama şu geldiğimizden beri sakalını düzeltip duruyor mesela. Hayır, hepsi de diğerleri onun sakalı varmış sanıyor, o manyak bir şey.
Arkadaşı bunun delirmeleriyle bağlantısını çözemediğini söyledi. O da normal sesiyle konuşmaya devam etti.
Anlasana, aynayı falan ayırt edemiyor mercekleri. Lönk diye kendilerini görüyorlar. Böyle, olduğu gibi...
Nedenmiş peki? Ne gerek varmış?
Ne bileyim be abicim! Ahiret soruları gibi.
Birasına bakarak dalıp gitti. Sonra masaya abanarak arkadaşına iyice yaklaştı. Bulanık, bir tünelin ucundaki biri gibi, şekli şemalı belirsiz bir adam.
Ben seni nereden tanıyorum ki ulan? Kimsin sen?
Belleği makineden çıkardılar. İki kişiydiler. Soruşturmadan sorumlu memurlar.
─ Baştan mı başlıyoruz, diye sordu belleği elinde tutan ilk memur.
─ Bir kere daha deneyelim ama bu sefer direkt aynayı sorarak başla, diye cevapladı ikinci memur.
─ Bence de. Yeterince düzgün çalışıyor.
Simülasyon yüklenirken, ayakta, biraz arkada duran ve alnını kaşıyan ikinci memur sormaktan kendisini alamadı:
─ Bu androidleri niye böyle bir olay yerine göndermişler ki? Belli tost olacakları. İsraf. Gidip biz baksak aynayı kırıp delilleri mahvetmek zorunda da kalmazlar.
Diğer memur sandalyesinde hafifçe dönecek oldu, o sırada soruyu bilgisayarın hoparlöründen teknisyen cevapladı.
Hangi işimizde bir yamukluk yok ki be abi.
Ama bir son değildi. Üstlerindeki tüm illüzyon dağıldığında ve çıplak, cinsiyetsiz, birbirinin aynı bedenleriyle kaldıklarında sıra dünyaya gelmişti.
Yere düştüler. Elleri -bütün bedeni gibi siyah turmalinden, boğumları çelikten- yere değdiği anda, metronun zemini dağıldı.
Yerdeki karolar öncesinde beyazdı ve çok parlaktı. Tepelerindeki floresan, ışığını olduğu gibi yansıtıyor, tek bir lekenin olmadığı ve tek bir tozun uçmadığı istasyonu aydınlatıyorlardı.
Duvarlara duyurular asılmıştı. Örneğin, yarın akşam kültür merkezinde 20.00’da başlayacak bir tekno blues festivalinin cıvıl cıvıl afişi vardı. Onun yanında daha geniş, sarı puntolu harflerle yazılmış, yatay siyah kesiklerle çerçevesi çizilmiş, bir platformdan düşen çöp adamın bulunduğu “Dikkat! Sarı bandı geçmeyin!” uyarısı. Biraz ilerisinde günlük resmi gazete, onun ilerisinde bir aksiyon filminin ve başka bir romantik komedi filminin afişleri, yapılacakların ve yapılmayacakların söylendiği küçük puntolu çeşitli duyurular... Duvar uzayıp giden bir panoydu. On, on beş metrede bir tekrarlanıyordu.
Tüm istasyonun eni yüz metre kadar. Genişliği on metre civarı.
Önlerinde, açık kapısından o mendebur aynanın gözüktüğü vagon duruyordu. Metro, istasyona sığmayacak kadar uzundu. Bir kılıcın keskinliğiyle uzanıyor ama yer yer vagonların ek yerleriyle bölünüyordu.
Hiçbir vagonda pencere olmadığı için metronun içi, içlerindekiler meçhuldü.
Sonrasında karolar zerrelerine ayrılarak yükseldi. Floresanın ışığında her yeri toza boğdular ve ortalığı gri bir sisin altına gömdüler. Çok kısa bir an. Afişleri dalgalandırmadılar. Dalgalandırmaya vakitleri olmadı. Yerlerinden söküp aldılar en fazla. Işık birkaç kere sönüp yanarak direndi. Son kez söndüğünde bir daha geri gelmedi.
Yine de etraf aydınlıktı. Kırmızı, her yere eşit dağılan soluk bir ışıkla.
Yer tamamen tele dönüşmüştü. Altında çapraz hatlarla desteklenmiş demir bir iskelet. Işık birkaç metreden daha fazla aşağıya uzanamıyordu. Sonsuzluğa giden bir uçurum.
Duvarın yerini aynı teller ve demir iskelet almıştı. Arkasında, birbirine vidalarla tutturulmuş demir plakalardan oluşan, üstünden geçen boruların ek yerlerinden bazen ince buharların çıktığı ve bir süre asılı kaldıktan sonra ağır, yağlı bir havayla sürüklendiği bir koridor.
Diğer tarafta paslanmış, pencerelerindeki camlar kırıldığı için demir plakalarla kapatılmış külüstür bir metro. Kapının karşısındaki aynadan her şey olduğu gibi yansıyordu.
Bir konteynırın içini andıran bir evde, gerçi gayet de birbirine eklenmiş konteynırlardan oluşan bir şehirde “andıran” demek doğru olmayacağı için düpedüz bir konteynırın içinde, masaya mum görüntüsü vermek için koyulmuş, yarı katı yağ atıklarından şekillendirilmiş kütleleri yakmayı deniyordu. Kafasında hayvan kıllarından yapılmış grili siyahlı bir peruk. Aynı kıllardan kendisine gür bir bıyık da yapmıştı.
Üstünde mavi çöp poşetlerinden yapılmış, kravatlı, şık bir takım.
Masanın ayakları yerine oradan buradan çıkmış parçalar konulmuştu: bir arabanın şaft mili, üst üste konulmuş ve üstünde yazı okunamayan tenekeler, boş kitaplar, boş gazete balyaları... Hiçbir şeye yazı yazılmıyordu, gerek yoktu da zaten çünkü merkez veri bankası onları fark ettirmeden, merceklerden giren veriyi sentezleyerek insanlar için dolduruyordu. Yani, androidler için. Farklı şekilde isimlendirmek bir fark yaratacaksa.
Onların mercekleri için değil. Bağlantıları çok önceden kopmuştu.
─ Hayatım, sofra hazır, diye bağırdı yatak odasındaki karısına.
Sofrada tabak yerine düz, bardak yerine bükülmüş, çatal ve bıçak yerine sivriltilmiş plakalar.
Karısı salonun kapısında durakladı ve ancak kulaklarına kadar uzanan, kocasınınkine benzeyen, cansız, ölü hayvanların kıllarından ibaret peruğunu eliyle düzeltti. Dudağını, daha doğrusu dudağının olması gereken yeri koyu kırmızı bir yağ tabakasıyla renklendirmeyi denemişti. Biraz da yanaklarına sürmüştü.
─ Nasıl olmuş, diye sordu.
Sesi tek düzeydi ama hafif bir neşe olduğunu hissettiğinize yemin edebilirdiniz.
Üzerinde, çöp poşetlerinin içini yazısız gazete kağıtlarıyla doldurarak yaptığı iki parça giysi.
─ Çok güzelsin, diyerek kravatını düzeltti kocası.
─ Sen de öylesin, sevgilim.
Yaklaşıp kocasını öptü. Kocası da onu. Sonra nazikçe elinden tutarak, sandalyesini geriye çekerek oturmasına yardım etti.
Sofrada yemek niyetine hiçbir şey yoktu. Gerek de yoktu zaten.
Konteynırın kapısı gürültüyle tekmelenip içeri iki memur girene kadar birbirlerine öyküler anlattılar. O gün neler yaptıklarını. İşten erken çıkıp yemyeşil çimenlerde gezdiklerini, uçurtma uçurduklarını, kadının nasıl o elbiseyi bulmak için saatlerce gezip yorulduğunu, kocasının kısa süreliğine işe dönüp nasıl başarılı bir hamleyle yaşanan krizi çözdüğünü ve kadının yanına döndükten sonra, alışveriş merkezinde oturdukları yeni dondurmacının dondurmalarının ne kadar lezzetli olduğunu, boğazlarının ağrımasından korktuklarını...
Akşam film izleyebilirlerdi, televizyonda -boş ve mat bir plaka- güzel bir film oynayacaktı.
İki memur. Çıplak bedenleriyle birbirinin aynı. Ellerindeki silahları onlara doğrultmuşlardı. Mum ışığında, tertemiz bir örtünün serili olduğu masada, bardaklarında şaraplarla oturan ve henüz sofranın ortasındaki hindiye dokunmamış çifti gördüklerinde bocaladılar.
Hiç de androidlere bilinçli olarak zarar verebilecek gibi gözükmüyorlardı.
─ Sessiz kalma hakkına sahipsiniz, diye bağırdı içeri giren ikinci memur. Söylediğiniz her şey...
Cümlesini bitiremedi. Yatak odasındaki, masanın üzerinden gördüğü o şey, onunla aynı hareketleri yapan android, yoksa, bir aynadaki yansıması mıydı?
Bütün illüzyon o anda dağılmaya başladı.
Not: Bu öykü ilk olarak 2020 yılında Esrarengiz Hikâyeler'de yayımlanmıştır.
-
 @ 32e18276:5c68e245
2023-12-06 15:29:43
@ 32e18276:5c68e245
2023-12-06 15:29:43I’m going to be on an ordinals panels as one of the people who is counter arguing the claim that they are good for bitcoin. I decided to brush up on the technicals on how inscriptions work. I am starting to see luke’s perspective on how it is exploiting a loophole in bitcoin’s anti-data-spam mechanisms.
Storing data in Bitcoin, the “standard” way
The standard way you add “data” to bitcoin is by calling the OP_RETURN opcode. Bitcoin devs noticed that people were storing data (like the bitcoin whitepaper) in the utxo set via large multisig transactions. The problem with this is that this set is unprunable and could grow over time. OP_RETURN outputs on the other-hand are provably prunable and don’t add to utxo bloat.
Here’s an excerpt from the march 2014 0.9.0 release notes that talks about this:
On OP_RETURN: There was been some confusion and misunderstanding in the community, regarding the OP_RETURN feature in 0.9 and data in the blockchain. This change is not an endorsement of storing data in the blockchain. The OP_RETURN change creates a provably-prunable output, to avoid data storage schemes – some of which were already deployed – that were storing arbitrary data such as images as forever-unspendable TX outputs, bloating bitcoin’s UTXO database. Storing arbitrary data in the blockchain is still a bad idea; it is less costly and far more efficient to store non-currency data elsewhere.
Much of the work on bitcoin core has been focused on making sure the system continues to function in a decentralized way for its intended purpose in the presence of people trying to abuse it for things like storing data. Bitcoin core has always discouraged this, as it is not designed for storage of images and data, it is meant for moving digital coins around in cyberspace.
To help incentive-align people to not do stupid things, OP_RETURN transactions were not made non-standard, so that they are relayable by peers and miners, but with the caveat:
- They can only push 40 bytes (later increased to 80,83, I’m guessing to support larger root merkle hashes since that is the only sane usecase for op_return)
Bitcoin also added an option called -datacarriersize which limits the total number of bytes from these outputs that you will relay or mine.
Why inscriptions are technically an exploit
Inscriptions get around the datacarriersize limit by disguising data as bitcoin script program data via OP_PUSH inside OP_IF blocks. Ordinals do not use OP_RETURN and are not subjected to datacarriersize limits, so noderunners and miners currently have limited control over the total size of this data that they wish to relay and include in blocks. Luke’s fork of bitcoin-core has some options to fight this spam, so hopefully we will see this in core sometime soon as well.
Inscriptions are also taking advantage of features in segwit v1 (witness discount) and v2/taproot (no arbitrary script size limit). Each of these features have interesting and well-justified reasons why they were introduced.
The purpose of the witness discount was to make it cheaper to spend many outputs which helps the reduction of the utxo set size. Inscriptions took advantage of this discount to store monke jpegs disguised as bitcoin scripts. Remember, bitcoin is not for storing data, so anytime bitcoin-devs accidentally make it cheap and easy to relay data then this should be viewed as an exploit. Expect it to be fixed, or at least provide tools to noderunners for fighting this spam.
Where do we go from here
The interesting part of this story is that people seem to attach value to images stored on the bitcoin blockchain, and they are willing to pay the fee to get it in the block, so non-ideologic miners and people who don’t care about the health and decentralization of bitcoin are happy to pay or collect the fee and move on.
Data should not get a discount, people should pay full price if they want to store data. They should just use op_return and hashes like opentimestamps or any other reasonable protocol storing data in bitcoin.
After going through this analysis I’ve come to the opinion that this is a pretty bad data-spam exploit and bitcoin devs should be working on solutions. Ideological devs like luke who actually care about the health and decentralization of the network are and I’m glad to see it.
-
 @ daa41bed:88f54153
2025-02-08 23:29:14
@ daa41bed:88f54153
2025-02-08 23:29:14Imagine a world where governments, long trusted to protect fiat currencies that can be printed without limit, openly declare that they trust a decentralized digital asset over traditional money. In recent months, that vision has begun to crystallize.
The Czech National Bank has signaled a gradual acceptance of digital assets as part of its broader monetary policy recalibration with changes to how capital gains taxes are handled on Bitcoin and a possible adoption by its central bank into its reserves stockpile. Simultaneously, El Salvador- once the poster child for Bitcoin as legal tender- has fine-tuned its policy framework at the behest of the WEF to no longer accept Bitcoin as legal tender. Meanwhile, several U.S. states have introduced bills to establish official Bitcoin reserves, and many are under active consideration. See Bitcoin Laws for a full breakdown of where these bills stand. Let's explore the pros of governments adopting strategic Bitcoin reserves.
Bitcoiners have long argued that the ultimate endorsement of Bitcoin comes when even the most established state institutions place their trust in it. Recent moves by several U.S. states—where lawmakers are proposing legislation to create official Bitcoin reserves—lend credence to this argument. When state governments start to codify the creation of a Bitcoin reserve, it signals that even entities steeped in traditional financial orthodoxy now recognize Bitcoin as a viable, strategic asset. For these states, it is imperative to accumulate hard assets like Bitcoin in reserves as they have no control over the monetary supply and, therefore, can suffer from debasement just as much as any citizen or sovereign nation not in control of their currency.
Suppose you have kept up with recent news that the Czech national bank was considering holding a considerable portion of their assets in Bitcoin. In that case, you understand the paradigm shift we are seeing. Banks are becoming less cautious in handling digital assets in a stark department, compared to previous dismissals of cryptocurrencies as genuine assets. While it is true that European Central Bank president Christine Lagarde wields considerable influence on monetary policy in Europe and may have put a temporary damper on the Czech central bank's aspirations for now (See Reuters), it should be evident that in the words of some Bitcoiners, "nothing stops this train." For Bitcoiners, such shifts validate the claim that Bitcoin's decentralized, algorithmic structure outperforms fiat systems, which are vulnerable to political manipulation and unchecked inflation. The Czech president's signing into law a bill removing capital gains tax from all Bitcoin held for at least three years proves that even those at the highest levels of policy creation are beginning to lose control of the narrative.
This state endorsement is more than symbolic. It is a strategic vote of confidence in Bitcoin's underlying technology—its transparent, immutable ledger and deflationary nature. When lawmakers and regulators in the United States start to invest public resources in Bitcoin, it undermines the decades-old narrative that only traditional assets like gold or oil are worthy of state backing. Instead, it repositions Bitcoin as an asset not just with a future but of the future. It can enhance and even replace all other existing reserve assets, lending further proof of Bitcoin as a store of value.
Bitcoin's capped supply is at the core of its appeal—only 21 million coins will ever exist. Bitcoiners assert that this scarcity is fundamental to Bitcoin's value proposition. A strategic Bitcoin reserve at any governmental level would effectively lock away a significant portion of the circulating supply, increasing its scarcity and further driving its price up.
Many in the Bitcoin and overall crypto community lauded President Bukele's 2021 announcement that his country would begin accumulating Bitcoin and giving it legal tender status. To Bitcoiners, it was a sign that governments were starting to see Bitcoin as a legitimate store of value, a medium of exchange, and vindication of everything they had fought for over the years. Of course, many will want to say that the country's acquisition of Bitcoin was simply a power play to get the World Economic Forum to come to the bargaining table, but if so, what? Here we are four years later, and El Salvador is no longer requiring Bitcoin as legal tender. This is not a step back, it is simply another example of why we are winning. I'll discuss this further in another article, but isn't it convenient that President Bukele continues to accumulate Bitcoin for his country after making a concession to the WEF for funds? Tick, tock, next block.
Bitcoiners view introducing reserve bills across U.S. states as a powerful mechanism for further tightening Bitcoin's available supply. Each government-held coin is one fewer coin available to the market, creating a scarcity premium. Market forces do not artificially impose this scarcity but are instead the natural outcome of an institution with deep pockets choosing to hold Bitcoin as a strategic asset. In a world where every coin in reserve represents a bulwark against inflation and economic uncertainty, Bitcoiners argue that this state-induced scarcity will profoundly affect Bitcoin's value over time. If you don't believe that to be the case, look at this chart of coins available on OTC desks last year, and let me tell you that you are not bullish enough. I'll explore the impact of OTC sales on price in a future article.

For years, Bitcoiners have decried the inherent weaknesses of fiat currencies—specifically, the ease with which governments can expand the money supply, leading to inflation and eroded purchasing power. Bitcoin, on the other hand, offers a fixed supply, decentralized issuance, and an ever-shrinking inflation rate that makes it immune to the government's printing press.
When a government opts for Bitcoin reserves, it makes a financial decision and a political statement. It says that the era of limitless money printing is over and that transparency, decentralization, and scarcity are the hallmarks of a sound monetary system. Institutional legitimacy is crucial for any asset that aspires to be a cornerstone of the global financial system.
When the United States, the world's largest economy, signals its intent to hold Bitcoin in its reserves, it sends a resounding message that can trigger a domino effect worldwide. The recent repeal of SAB121 by the Securities and Exchange Commission is a step in the right direction, by now allowing companies and course, governments at every level to accumulate Bitcoin into their reserves. When central banks like the Czech National Bank begin to signal openness toward digital assets, it paves the way for broader institutional participation. Once wary of the volatile digital asset market, financial institutions, asset managers, and even pension funds are gradually warming up to Bitcoin.
We cannot underestimate what sort of network effect this will have on Bitcoin as its utility and value proposition become more robust as a result of state-level adoption. Bitcoiners believe that such a shift will cement Bitcoin's status as a universally accepted and trusted store of value, capable of challenging—and eventually surpassing—traditional reserve assets like gold and fiat currencies.
One of the most enduring arguments among Bitcoiners is that Bitcoin is the digital successor to gold. For centuries, gold has been the haven, the ultimate store of value during times of crisis. Bitcoin, with its fixed supply and digital accessibility, is ideally positioned to take over that role in the modern era. A state-backed Bitcoin reserve would serve as this narrative's definitive stamp of approval. If a government is willing to set aside billions of dollars in a digital asset, it must believe that this asset can preserve and even appreciate its value over time. Such a move would provide a critical psychological boost to the market, as both retail and institutional investors begin to see Bitcoin as not just a speculative tool but as the modern equivalent of a haven set. Gold continues to appreciate this year while Bitcoin remains relatively flat. How long until we see it decouple from the markets and witness price appreciation not seen since the last halving?
I hope you enjoyed reading this lengthy article on the pros of governments adopting a strategic Bitcoin reserve. If you'd like to chime in, you can find me on Nostr via @geek on Primal, or via my npub anywhere else. In part two, I will examine the other side of the debate, the cons, and the potential pitfalls of such a policy. Stay tuned!
-
 @ 8fb140b4:f948000c
2023-11-21 21:37:48
@ 8fb140b4:f948000c
2023-11-21 21:37:48Embarking on the journey of operating your own Lightning node on the Bitcoin Layer 2 network is more than just a tech-savvy endeavor; it's a step into a realm of financial autonomy and cutting-edge innovation. By running a node, you become a vital part of a revolutionary movement that's reshaping how we think about money and digital transactions. This role not only offers a unique perspective on blockchain technology but also places you at the heart of a community dedicated to decentralization and network resilience. Beyond the technicalities, it's about embracing a new era of digital finance, where you contribute directly to the network's security, efficiency, and growth, all while gaining personal satisfaction and potentially lucrative rewards.
In essence, running your own Lightning node is a powerful way to engage with the forefront of blockchain technology, assert financial independence, and contribute to a more decentralized and efficient Bitcoin network. It's an adventure that offers both personal and communal benefits, from gaining in-depth tech knowledge to earning a place in the evolving landscape of cryptocurrency.
Running your own Lightning node for the Bitcoin Layer 2 network can be an empowering and beneficial endeavor. Here are 10 reasons why you might consider taking on this task:
-
Direct Contribution to Decentralization: Operating a node is a direct action towards decentralizing the Bitcoin network, crucial for its security and resistance to control or censorship by any single entity.
-
Financial Autonomy: Owning a node gives you complete control over your financial transactions on the network, free from reliance on third-party services, which can be subject to fees, restrictions, or outages.
-
Advanced Network Participation: As a node operator, you're not just a passive participant but an active player in shaping the network, influencing its efficiency and scalability through direct involvement.
-
Potential for Higher Revenue: With strategic management and optimal channel funding, your node can become a preferred route for transactions, potentially increasing the routing fees you can earn.
-
Cutting-Edge Technological Engagement: Running a node puts you at the forefront of blockchain and bitcoin technology, offering insights into future developments and innovations.
-
Strengthened Network Security: Each new node adds to the robustness of the Bitcoin network, making it more resilient against attacks and failures, thus contributing to the overall security of the ecosystem.
-
Personalized Fee Structures: You have the flexibility to set your own fee policies, which can balance earning potential with the service you provide to the network.
-
Empowerment Through Knowledge: The process of setting up and managing a node provides deep learning opportunities, empowering you with knowledge that can be applied in various areas of blockchain and fintech.
-
Boosting Transaction Capacity: By running a node, you help to increase the overall capacity of the Lightning Network, enabling more transactions to be processed quickly and at lower costs.
-
Community Leadership and Reputation: As an active node operator, you gain recognition within the Bitcoin community, which can lead to collaborative opportunities and a position of thought leadership in the space.
These reasons demonstrate the impactful and transformative nature of running a Lightning node, appealing to those who are deeply invested in the principles of bitcoin and wish to actively shape its future. Jump aboard, and embrace the journey toward full independence. 🐶🐾🫡🚀🚀🚀
-
-
 @ de496884:72617b81
2023-11-20 13:54:02
@ de496884:72617b81
2023-11-20 13:54:02Hola nostriches. Hoy quiero hacer una publicación a modo de acercamiento al surgimiento de las categorías de género y feminismo. Así que si te interesa el tema haz un esfuerzo, quédate y lee hasta el final.
El «nuevo» feminismo surge en los años 60 en aquellos países desarrollados que acordaron el reconocimiento a los derechos humanos contenidos en la declaración respectiva de la ONU. Entonces, como extensión a dicho reconocimiento es que se gesta el movimiento feminista. A partir de entonces, se vuelve a plantear la relación entre naturaleza y cultura y se llega a la conclusión de que las diferencias sociales van más allá de las diferencias biológicas, lo cual tiene que ver con que hasta la satisfacción de las necesidades elementales como son la alimentación, la vivienda o el vestuario, están condicionadas por construcciones sociales.
Pues resulta que una de las primeras propuestas identificó la subordinación femenina producto de una organización patriarcal, tomando la categoría patriarcado de Max Weber. Es así como la visión de patriarcado se extendió al discurso político y académico. Sin embargo, no existía información acerca del desarrollo histórico de dicha categoría, sistematización, variaciones, etc., debido a que era algo que recién se percibía en sociedad.
Sin embargo, la misma categoría de patriarcado junto a la de relaciones de poder para explicar fenómenos sociales contemporáneos, constituye uno de los principales aportes del feminismo. Es así como han logrado primero visibilizar y luego deconstruir y desmontar una serie de patrones existentes en la cultura que hacían a la mujer subordinarse al hombre, y que estaban presentes en el sistema sexo/género.
 Imagen relativa a la lucha contra el patriarcado
Imagen relativa a la lucha contra el patriarcadoHasta ese momento, en las investigaciones de corte sociológico se podía observar un androcentrismo excesivo al dar cuenta de que el discurso científico giraba en torno al hombre como sujeto y objeto de la investigación. Incluso para muchos positivistas como el mismo Weber, los problemas relativos a las mujeres quedaban en un segundo plano y eran achacados a una supuesta pasividad en el ámbito doméstico-familiar. Dicha pasividad partía de la supuesta inferioridad biológica del género femenino.
El patriarcado entonces era una categoría vacía en sí misma, sin valor explicativo. Desde el punto de vista político pudo ser útil para la movilización pero no resistió la polémica de los críticos del feminismo ni problematizó los conflictos a ser resueltos. Pero por otro lado, un grupo de mujeres -académicas principalmente- se puso manos a la obra en una tarea más pequeña pero con mayores resultados a la larga. Se propusieron generar conocimientos sobre las condiciones de vida de la mujer, buscar en el pasado y el presente los aportes de las mujeres a la sociedad, hacerlas visibles en la historia. Es así como surgen centros académicos, ONG, proyectos, centros de estudios sobre la mujer, etc.
Convendría distinguir entonces dos posturas que acompañaron a la investigación sobre las mujeres: uno que toma como objeto de estudio a la mujer; condiciones de vida, trabajo, cultura, y otra que privilegia a la sociedad como generadora de la subordinación de las mujeres. Mientras la primera perspectiva generaba conocimiento sobre las mujeres en el estudio de las relaciones mujer-hombre y mujer-mujer, la segunda tenía una visión más holística ya que planteaba que hay que estudiar la sociedad ya que la subordinación de las mujeres es producto de la organización de esta, y que no se avanzará solamente estudiando a las mujeres, pues el estudio debe ser más amplio y en diferentes niveles, ámbitos y tiempos.
Es en esta búsqueda donde nace y se desarrolla el concepto de género como categoría social. Es así que los sistemas de género/sexo fueron entendidos como conjuntos de prácticas, símbolos, representaciones, normas y valores sociales que las sociedades construyen a partir de la diferencia anatomofisiológica y que dotan de sentido a los impulsos sexuales, la reproducción y en general a las relaciones de las personas. Por tanto, este sistema pasó a ser el objeto de estudio para comprender la subordinación de la mujer al hombre. Al ser el reconocimiento de una dimensión de la desigualdad social hasta entonces desconocida, se considera la ruptura epistemológica más importante de la segunda mitad del siglo pasado.
 Imagen representativa del binarismo de género
Imagen representativa del binarismo de géneroHay que decir que los fenómenos sociales se definen por la relación que guardan entre sí. Es así que la contextualización adquiere gran importancia. Varones y hembras tenemos la capacidad de producir con el cuerpo, pero solo los cuerpos de las hembras pueden gestar y por tanto asegurar la especie humana. Todo grupo humano que pretenda sobrevivir debe asegurarse cierto número de hembras que lo hagan posible. De ahí un poder particular del cuerpo de las hembras que además es económicamente útil. Dicho poder no es en tanto entidad biológica, sino que es la sociedad la que le otorga este poder. En este punto es importante preguntarnos históricamente ¿quiénes han controlado la capacidad reproductiva de las mujeres?, ¿quiénes han tenido la preferencia en el acceso sexual? Para asegurar un control efectivo sobre la reproducción es necesario asegurar el acceso a la sexualidad.
Ello también lleva a dirigir el trabajo que hacen porque de lo contrario, las mujeres pudieran tener espacio para representar una amenaza al dominio de los hombres. Es importante atender a las etapas del desarrollo de las mujeres, que permitirá ver cómo se moldean para aceptar la desigualdad y las jerarquías según el género en las distintas sociedades y culturas.
Otro contexto a delimitar es el ámbito doméstico donde históricamente ha estado ubicada la subordinación femenina. Se ha puesto al descubierto que en mujeres que comparten la misma posición de clase y raza, la condición femenina se redefine a lo largo de la vida y que algunas mujeres gozan de poder sobre otras aún en contextos de alta dominación masculina, donde se les inviste de autoridad, creando el sistema zonas de incertidumbre que las divide como género e impide alianzas y se legitima la dominación. Foucault decía que «el poder se ejerce, no se posee», siempre está en peligro de perderse y no basta con normas, leyes, amenazas o castigos. De ahí que los espacios de subordinación sean también espacios de poder de las mujeres. Es en estos espacios donde aparece la inseguridad, la tensión, la confrontación y por ejemplo, las mujeres pueden reclamar la anticoncepción.
Para terminar, es importante tener en cuenta que el género es una forma de desigualdad social que siempre está articulado con otras formas de desigualdad ya sea clase, raza, grupo etario, etc. Hay que pensar la dominación masculina con un comienzo vago en el tiempo, pero que permite desligar la subordinación de las mujeres de la evolución «natural» de la humanidad y entenderla como un proceso histórico. En ese sentido es necesario destacar que, respecto a la raza, en sociedades plurales hay que atender al contexto étnico-cultural ya que en dependencia de las relaciones entre personas de razas distintas, estarán condicionadas las relaciones entre los géneros.
 Imagen de mujeres de distintas razas
Imagen de mujeres de distintas razasPor otro lado, si bien es sabido que históricamente el sistema de género social imperante ha contribuido a invisibilizar a la mujer, asociar necesariamente dicha categoría únicamente a ella, lo que hace es nuevamente recrear el absolutismo histórico que tanto daño ha hecho, ahora como lo antagónico al hombre. En la construcción social participan todos los individuos presentes en el sistema género.
Hasta aquí la publicación de hoy, de la cual aun se puede ahondar mucho más, sobre todo en lo referido al origen de la dominación o de la jerarquización del binomio «hombre/mujer» desde un punto de vista antropológico, pero eso quedará pendiente para otro momento. ¡Así que hasta la próxima!, ¡nos vemos en Nostr!
........................................
English version
Hello nostriches. Today I want to make a post by way of an approach to the emergence of the categories of gender and feminism. So if you are interested in the topic make an effort, stay and read to the end.
The "new" feminism emerged in the 60's in those developed countries that agreed to recognize the human rights contained in the respective UN declaration. Then, as an extension of that recognition, the feminist movement was born. From then on, the relationship between nature and culture was raised again and the conclusion was reached that social differences go beyond biological differences, which has to do with the fact that even the satisfaction of elementary needs such as food, housing or clothing are conditioned by social constructions.
It turns out that one of the first proposals identified female subordination as a product of a patriarchal organization, taking Max Weber's category of patriarchy. This is how the vision of patriarchy was extended to political and academic discourse. However, there was no information about the historical development of this category, systematization, variations, etc., because it was something that was only recently perceived in society.
However, the same category of patriarchy, together with that of power relations to explain contemporary social phenomena, constitutes one of the main contributions of feminism. This is how they have first made visible and then deconstructed and dismantled a series of existing patterns in the culture that made women subordinate to men, and that were present in the sex/gender system.
 Image relating to the fight against patriarchy
Image relating to the fight against patriarchyUp to that time, in sociological research, an excessive androcentrism could be observed as scientific discourse revolved around men as the subject and object of research. Even for many positivists such as Weber himself, the problems related to women remained in the background and were blamed on a supposed passivity in the domestic-family sphere. This passivity was based on the supposed biological inferiority of the female gender.
Patriarchy was then an empty category in itself, with no explanatory value. From the political point of view, it could be useful for mobilization, but it did not resist the polemic of feminism's critics, nor did it problematize the conflicts to be resolved. But on the other hand, a group of women - mainly academics - set to work on a smaller task but with greater results in the long run. They set out to generate knowledge about women's living conditions, to search in the past and present for women's contributions to society, to make them visible in history. This is how academic centers, NGOs, projects, women's studies centers, etc., came into being.
It would be convenient to distinguish then two postures that accompanied the research on women: one that takes women as the object of study; living conditions, work, culture, and the other that privileges society as the generator of women's subordination. While the first perspective generated knowledge about women in the study of woman-man and woman-woman relations, the second had a more holistic vision, since it proposed that society must be studied, since the subordination of women is a product of its organization, and that progress will not be made only by studying women, since the study must be broader and at different levels, spheres and times.
It is in this search that the concept of gender as a social category was born and developed. Thus, gender/sex systems were understood as a set of practices, symbols, representations, norms and social values that societies construct on the basis of anatomophysiological differences and that give meaning to sexual impulses, reproduction and, in general, to people's relationships. Therefore, this system became the object of study to understand the subordination of women to men. As the recognition of a hitherto unknown dimension of social inequality, it is considered the most important epistemological breakthrough of the second half of the last century.
 Representative image of gender binarism
Representative image of gender binarismIt must be said that social phenomena are defined by their relationship with each other. Thus, contextualization acquires great importance. Males and females have the capacity to produce with their bodies, but only the bodies of females can gestate and therefore ensure the human species. Any human group that intends to survive must ensure a certain number of females to make it possible. Hence a particular power of the female body, which is also economically useful. This power is not as a biological entity, but it is society that gives it this power. At this point it is important to ask ourselves historically, who has controlled the reproductive capacity of women, who has had the preference in sexual access? To ensure effective control over reproduction, it is necessary to ensure access to sexuality.
 Allegorical image of pregnancy
Allegorical image of pregnancyThis also leads to directing the work they do because otherwise, women may have room to pose a threat to men's dominance. It is important to pay attention to the stages of women's development, which will allow us to see how they are shaped to accept inequality and gender hierarchies in different societies and cultures.
Another context to delimit is the domestic sphere where female subordination has historically been located. It has been discovered that in women who share the same class and race position, the feminine condition is redefined throughout life and that some women enjoy power over others even in contexts of high male domination, where they are invested with authority, creating the system of uncertainty zones that divide them as a gender and prevent alliances and legitimize domination. Foucault said that "power is exercised, not possessed", it is always in danger of being lost and norms, laws, threats or punishments are not enough. Hence, the spaces of subordination are also spaces of women's power. It is in these spaces where insecurity, tension, confrontation appear and where, for example, women can demand contraception.
To conclude, it is important to keep in mind that gender is a form of social inequality that is always articulated with other forms of inequality, be it class, race, age group, etc. It is necessary to think of male domination with a vague beginning in time, but which allows us to separate the subordination of women from the "natural" evolution of humanity and to understand it as a historical process. In this sense, it is necessary to emphasize that, with respect to race, in plural societies it is necessary to pay attention to the ethno-cultural context since, depending on the relations between people of different races, the relations between genders will be conditioned.
 Image of women of different races
Image of women of different racesOn the other hand, although it is known that historically the prevailing social gender system has contributed to make women invisible, to necessarily associate this category only to women is to recreate the historical absolutism that has done so much damage, this time as antagonistic to men. All individuals present in the gender system participate in the social construction.
So much for today's publication, of which we can still go much deeper, especially with regard to the origin of domination or the hierarchization of the binomial "man/woman" from an anthropological point of view, but that will be left for another time. So until next time, see you in Nostr!
Créditos | Credits
Bibliografía consultada | Consulted bibliography:
-
Barbieri, T. (1993). Sobre la categoría género. Una introducción teórico-metodológica. Debates en Sociología. (18). 1-19. https://doi.org/10.18800/debatesensociologia.199301.006
-
Echevarría, D. (2020). Desigualdades de género e interseccionalidad. Análisis del contexto cubano 2008-2018. Facultad Latinoamericana de Ciencias Sociales (Programa-Cuba). https://www.clacso.org.ar/libreria-latinoamericana-cm/libro_detalle_resultado.php?id_libro=2346&campo=cm&texto=248
Traducción | Translation:
DeepL
-
-
 @ a012dc82:6458a70d
2025-02-08 22:44:44
@ a012dc82:6458a70d
2025-02-08 22:44:44The world of cryptocurrency has always been a rollercoaster of highs and lows, but recent developments in the Bitcoin market have caught the attention of investors worldwide. The circulating supply of Bitcoin in profit has surged to a multi-year high, a phenomenon not seen since the heady days of November 2021 when Bitcoin reached its all-time high. This significant milestone, backed by data from industry analysts at Glassnode and a detailed report from Bitfinex, paints a picture of a robust Bitcoin market. The implications of this surge are far-reaching, affecting not just seasoned cryptocurrency traders but also new investors who are contemplating dipping their toes into the Bitcoin pool. This article aims to dissect this trend, exploring its roots, its impact on the market, and what it potentially spells out for the future of Bitcoin investment.
Table Of Content
-
Understanding the Surge
-
Implications for Long-term Investors
-
Market Strength and Investor Confidence
-
Potential Early Signs of a Bull Market
-
Caution and Market Dynamics
-
Conclusion
-
FAQs
Understanding the Surge
The surge in Bitcoin's circulating supply in profit is a complex phenomenon, driven by a confluence of market dynamics and investor behavior. The recent increase in Bitcoin's price, which saw it soar above $37,000, is a primary factor. This price hike has pushed a significant portion of Bitcoin into profitable territory. According to the Bitfinex report, over 16.3 million Bitcoin, a staggering amount by any measure, are currently in profit. This figure is considerably higher than the historical average, suggesting a market that is not only recovering but thriving. The surge is not just a momentary blip but a reflection of deeper market trends, including increased institutional interest in Bitcoin, broader acceptance of cryptocurrencies as a legitimate asset class, and the growing perception of Bitcoin as a hedge against inflation and currency devaluation.
Implications for Long-term Investors
For long-term investors, this surge in Bitcoin's profitability is a beacon of stability in the typically volatile cryptocurrency market. The fact that 70% of Bitcoin's total circulating supply has remained static over the past year is indicative of a maturing market where investors are increasingly viewing Bitcoin as a long-term investment rather than a quick profit opportunity. This holding pattern contributes to a tightening of supply, which, coupled with increasing demand, can lead to a sustained price increase. However, long-term investors should also be aware of the potential risks. The cryptocurrency market is still relatively young and can be influenced by regulatory changes, technological advancements, and shifts in investor sentiment. Therefore, while the current trend is encouraging, it should be viewed within the broader context of market dynamics.
Market Strength and Investor Confidence
The current state of the Bitcoin market is a testament to its growing strength and the confidence it instills in investors. With a majority of holders seeing positive returns, there's a renewed vigor in the market, attracting both retail and institutional investors. This influx of new investment can further stabilize the market and potentially drive prices higher. However, this increased investor confidence must be tempered with a degree of caution. The cryptocurrency market is known for its rapid fluctuations, and what goes up can just as quickly come down. Investors should be mindful of the inherent risks and conduct thorough research before making any investment decisions. The market's strength, while promising, is not a guarantee of future performance, and a prudent investment strategy should always be in place.
Potential Early Signs of a Bull Market
The analysis by Bitfinex suggests that the market might be in the early stages of a bull market. This is a significant indicator for investors, as bull markets are characterized by rising prices and increased buying activity. If this trend continues, it could lead to substantial gains for those invested in Bitcoin. However, predicting market movements, especially in the volatile world of cryptocurrencies, is fraught with uncertainty. While the signs are positive, they are not infallible indicators of future performance. Investors should therefore approach this potential bull market with optimism tempered by realism, recognizing that market conditions can change rapidly and without warning.
Caution and Market Dynamics
In the face of these optimistic trends, a word of caution is warranted. The cryptocurrency market is notoriously unpredictable, and while the current indicators are positive, they are not immune to sudden and unexpected changes. Factors such as regulatory announcements, technological breakthroughs, or macroeconomic shifts can rapidly alter the market landscape. Therefore, investors should remain vigilant, keeping abreast of market news and trends. Diversification of investments, a keen understanding of market dynamics, and a clear investment strategy are essential tools in navigating the complexities of the Bitcoin market.
Conclusion
The surge in Bitcoin's circulating supply in profit to a multi-year high marks a significant milestone in the cryptocurrency's journey. It reflects a market that is gaining maturity, strength, and the confidence of its investors. This development could herald the beginning of a new era for Bitcoin, characterized by stability and sustained growth. However, the path of Bitcoin and the broader cryptocurrency market remains unpredictable. Investors should therefore approach this market with a well-informed strategy, balancing optimism with a healthy dose of caution. In the ever-evolving world of cryptocurrency, staying informed and adaptable is key to navigating the market's highs and lows.
FAQs
How does this surge affect long-term investors? Long-term investors may see this as a sign of market stability and maturity, indicating that Bitcoin is increasingly being viewed as a viable long-term investment.
Could this trend indicate the start of a Bitcoin bull market? While the surge in profitable Bitcoin supply could be an early sign of a bull market, predicting market movements in the volatile cryptocurrency sector is complex and uncertain.
What percentage of Bitcoin's circulating supply is currently in profit? Over 83% of Bitcoin's circulating supply is reported to be in profit, according to recent data.
What should investors be cautious about in light of this surge? Investors should be aware of the inherent volatility in the cryptocurrency market and consider factors like regulatory changes, technological advancements, and broader market dynamics before making investment decisions.
How does the current Bitcoin market compare to historical averages? The current percentage of Bitcoin in profit is significantly higher than the historical average, indicating a particularly strong market phase.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 8fb140b4:f948000c
2023-11-18 23:28:31
@ 8fb140b4:f948000c
2023-11-18 23:28:31Chef's notes
Serving these two dishes together will create a delightful centerpiece for your Thanksgiving meal, offering a perfect blend of traditional flavors with a homemade touch.
Details
- ⏲️ Prep time: 30 min
- 🍳 Cook time: 1 - 2 hours
- 🍽️ Servings: 4-6
Ingredients
- 1 whole turkey (about 12-14 lbs), thawed and ready to cook
- 1 cup unsalted butter, softened
- 2 tablespoons fresh thyme, chopped
- 2 tablespoons fresh rosemary, chopped
- 2 tablespoons fresh sage, chopped
- Salt and freshly ground black pepper
- 1 onion, quartered
- 1 lemon, halved
- 2-3 cloves of garlic
- Apple and Sage Stuffing
- 1 loaf of crusty bread, cut into cubes
- 2 apples, cored and chopped
- 1 onion, diced
- 2 stalks celery, diced
- 3 cloves garlic, minced
- 1/4 cup fresh sage, chopped
- 1/2 cup unsalted butter
- 2 cups chicken broth
- Salt and pepper, to taste
Directions
- Preheat the Oven: Set your oven to 325°F (165°C).
- Prepare the Herb Butter: Mix the softened butter with the chopped thyme, rosemary, and sage. Season with salt and pepper.
- Prepare the Turkey: Remove any giblets from the turkey and pat it dry. Loosen the skin and spread a generous amount of herb butter under and over the skin.
- Add Aromatics: Inside the turkey cavity, place the quartered onion, lemon halves, and garlic cloves.
- Roast: Place the turkey in a roasting pan. Tent with aluminum foil and roast. A general guideline is about 15 minutes per pound, or until the internal temperature reaches 165°F (74°C) at the thickest part of the thigh.
- Rest and Serve: Let the turkey rest for at least 20 minutes before carving.
- Next: Apple and Sage Stuffing
- Dry the Bread: Spread the bread cubes on a baking sheet and let them dry overnight, or toast them in the oven.
- Cook the Vegetables: In a large skillet, melt the butter and cook the onion, celery, and garlic until soft.
- Combine Ingredients: Add the apples, sage, and bread cubes to the skillet. Stir in the chicken broth until the mixture is moist. Season with salt and pepper.
- Bake: Transfer the stuffing to a baking dish and bake at 350°F (175°C) for about 30-40 minutes, until golden brown on top.
-
 @ c1e6505c:02b3157e
2025-02-08 21:52:51
@ c1e6505c:02b3157e
2025-02-08 21:52:51***"Time is the best teacher but unfortunately it kills all of its students."*** I'm currently visiting my dad for a few days as I had to take my car in for some repairs and maintenance, which included an oil gasket leak, power steering fluid flush, brake fluid flush, spark plugs, and the works. The process took a couple of hours to complete, so instead of waiting in the waiting room or having someone pick me up to go wait comfortably at home, I decided to walk around with my camera and try to make some new work. I have to say, there's really nothing more that I enjoy than walking aimlessly in an area that I have never been and taking photographs. *I love it.* I lose myself and everything that is on my mind that I "worry" about. I'm present, in the zone, and honestly having a great time. Photography for me is a portal to enter a state of mind that transcends time and space. The area that I was in was very industrial, so my walk started next door at the other car mechanic shop, and I meandered down to the small local town where some shops were. Didn't see too much, so I turned around and started walking back down the other way. Sometimes I don't see anything of interest for a while. What I have noticed though, as a little trick to start having things "come out of the woodwork," is just to start shooting at the first thing that captures my interest. Getting the ball rolling with pushing the shutter somehow gets me in the "flow state" that I enjoy getting in when making photographs. \[ \]( As I walked further, I visited a plant nursery that was just opening. The woman who was opening the gate was very nice and invited me into walk around and do as I please. There were a few nice plants around, but what gravitates me the most is seemingly, to others maybe, the "ugly stuff" or the subject matter that one wouldn’t really consider making a photograph of. Blank spaces, trash, neglect - it's all good stuff to me. The light falling upon these subjects makes them interesting. After the nursery, I found a large industrial facility and a train yard. A worker stood next to one of the train cars, so I went up and asked what they were loading. He said that he’s been working there for 30 years, and that they make plastic trash bags, and those tubes feeding into the train cars were pumping out plastic beads for production. I thought that was interesting. We chatted for a bit, I thanked him for his time, and moved on.           Eventually, I ended up at a church with these really nice orange and brown doors. I sat on a bench in the back to kill some time, listening to a few podcasts. While I was there, I noticed a sign that read: *"Happy moments, praise God. Difficult moments, seek God. Quiet moments, worship God. Painful moments, trust God. Every moment, thank God."* I’m not a religious guy per se, haven’t been to church in over a decade, and I’ve had my own experiences — psychedelics included — where I’ve glimpsed something I’d call “God.”, but there’s something to take from that. Whatever your definition of “God” is, there’s value in gratitude whether things are good or bad. Life itself is a miracle. Appreciating the small things keeps you grounded, humble, and connected.   ) *Just in case you missed it…* **I have a limited edition framed print that I will have available until February 28th.** Only two will be made, and they will come framed; one in black, one in silver. If you enjoy my work, this would be a great collectors piece. \]() ***I shoot with a Leica M262, and edit in Lightroom + Dehancer*** [***Use “PictureRoom” for 10% off Dehancer Film***](https://www.dehancer.com/shop/pslr/film) If you’ve made it this far, thank you for taking the time to view my work - I appreciate it. Please consider becoming a paid subscriber to support my work. Also, please contact me if you would like to purchase any of my prints.  [Dehancer Film (promo code "PICTUREOOM")](https://www.dehancer.com/shop/pslr/film) *If you've found value in this newsletter, I'd be incredibly grateful for your support. While these posts will always be freely available, becoming a paid subscriber helps ensure I can continue delivering quality content to your inbox. Share this newsletter with friends, leaving a comment, or simply hitting the 'like' button all make a difference.* Thank you - Colin
-
 @ 8fb140b4:f948000c
2023-11-02 01:13:01
@ 8fb140b4:f948000c
2023-11-02 01:13:01Testing a brand new YakiHonne native client for iOS. Smooth as butter (not penis butter 🤣🍆🧈) with great visual experience and intuitive navigation. Amazing work by the team behind it! * lists * work
Bold text work!

Images could have used nostr.build instead of raw S3 from us-east-1 region.
Very impressive! You can even save the draft and continue later, before posting the long-form note!
🐶🐾🤯🤯🤯🫂💜
-
 @ 32e18276:5c68e245
2025-02-08 20:20:46
@ 32e18276:5c68e245
2025-02-08 20:20:46This period of the Damus OpenSats grant has been productive, and encompasses the work past our alpha release of Notedeck. Since we sent our last report on Dec 5, this encompasses all the work after then.
Damus is supported by the OpenSats LTS grant, which allows us to continue working on the goodies below. Thank you!
Damus Notedeck
Added
- Initial algo timelines (William Casarin) #712
- Initial support for local-network P2P nostr: multicast support (William Casarin) #626
- First steps toward the notedeck browser: multiple app support #565
- Clicking a mention now opens profile page (William Casarin) 5a241d730
- Note previews when hovering reply descriptions (William Casarin) #591
-
Various Android updates and compatibility improvements (Ken Sedgwick, William Casarin)
-
Media uploads (kernelkind) #662
- Profile editing (kernelkind) #625
- Add hashtags to posts (Daniel Saxton) #592
- Enhanced command-line interface for user interactions (Ken Sedgwick)
- Debug features for user relay-list and mute list synchronization (Ken Sedgwick)
Changed
- Major timeline cache refactor (William Casarin) #653
- Increased ping intervals for network performance (William Casarin)
- Migrated to egui v0.29.1 (William Casarin) #551
- Switch to only notes & replies on some tabs (William Casarin) #598
- Only show column delete button when not navigating (William Casarin)
- Pointer interactions enhancements in UI (William Casarin)
- Show profile pictures in column headers (William Casarin)
-
Show usernames in user columns (William Casarin)
-
Add confirmation when deleting columns (kernelkind)
- Enhance Android build and performance (Ken Sedgwick)
- Image cache handling using sha256 hash (kieran)
- Introduction of decks_cache and improvements (kernelkind)
- Nostrdb update for async support (Ken Sedgwick)
- Persistent theme setup across sessions (kernelkind)
- Tombstone muted notes (Ken)
Fixed
- Fix GIT_COMMIT_HASH compilation issue (William Casarin)
- Fix avatar alignment in profile previews (William Casarin)
- Fix broken quote repost hitbox (William Casarin)
- Fix crash when navigating in debug mode (William Casarin)
- Fix long delays when reconnecting (William Casarin)
-
Fix repost button size (William Casarin)
-
Fixed since kind filters (kernelkind)
- Clippy warnings resolved (Dimitris Apostolou)
Damus iOS
Work continued on the iOS side. While I was not directly involved in the work since the last report, I have been directing and managing its development.
Added
- Render Gif and video files while composing posts (Swift Coder)
- Purple members who have been active for more than a year now get a special badge (Daniel D’Aquino)
- Add profile info text in stretchable banner with follow button (Swift Coder)
- Paste Gif image similar to jpeg and png files (Swift Coder)
Changed
- Improved clarity of the mute button to indicate it can be used for blocking a user (Daniel D’Aquino)
- Made the microphone access request message more clear to users (Daniel D’Aquino)
- Improved UX around the label for searching words (Daniel D’Aquino)
- Improved accessibility support on some elements (Daniel D’Aquino)
Fixed
- Fixed issue where the "next" button would appear hidden and hard to click on the create account view (Daniel D’Aquino)
- Fix non scrollable wallet screen (Swift Coder)
- Fixed suggested users category titles to be localizable (Terry Yiu)
- Fixed GradientFollowButton to have consistent width and autoscale text limited to 1 line (Terry Yiu)
- Fixed right-to-left localization issues (Terry Yiu)
- Fixed AddMuteItemView to trim leading and trailing whitespaces from mute text and disallow adding text with only whitespaces (Terry Yiu)
- Fixed SideMenuView text to autoscale and limit to 1 line (Terry Yiu)
- Fixed an issue where a profile would need to be input twice in the search to be found (Daniel D’Aquino)
- Fixed non-breaking spaces in localized strings (Terry Yiu)
- Fixed localization issue on Add mute item button (Terry Yiu)
- Replace non-breaking spaces with regular spaces as Apple's NSLocalizedString macro does not seem to work with it (Terry Yiu)
- Fixed localization issues in RelayConfigView (Terry Yiu)
- Fix duplicate uploads (Swift Coder)
- Remove duplicate pubkey from Follow Suggestion list (Swift Coder)
- Fix Page control indicator (Swift Coder)
- Fix damus sharing issues (Swift Coder)
- Fixed issue where banner edit button is unclickable (Daniel D’Aquino)
- Handle empty notification pages by displaying suitable text (Swift Coder)
Nostrdb
nostrdb, the engine that powers notecrumbs, damus iOS, and notedeck, continued to improve:
Added
- Added nip50 fulltext searching (William Casarin) #68, demo
- Added async migrations (William Casarin) #59
- Implement author queries (William Casarin) #57
- Make
ndbthreadsafe (William Casarin) #56
Nostrdb Rust
Our nostrdb rust bindings also had improvements
- Async! Adding efficient, poll-based stream support (William Casarin): #25
Notecrumbs
Notecrumbs, the njump-style opengraph server that powers the damus.io links, got an update that upgraded it to async nostrdb
- Switch to async nostrdb-rs (William Casarin) #16
How money was used
- relay.damus.io server costs
- Living expenses
Next quarter
Our goal for next update: zaps, android version, lists, outbox model for notedeck. Olas images in damus iOS, continue switching Damus iOS over to local relay model so we can add outbox support.
-
 @ 25c48353:bbf9841d
2025-02-08 23:44:56
@ 25c48353:bbf9841d
2025-02-08 23:44:56One way parents can protect their children in cyberspace is by knowing what cyberspaces your children like to engage with. Today, we'll explore 4 apps that the DOJ has found criminals on.
Here are the apps
- Cash App
- Valorant
- Discord
- Telegram
Background on the Data
At Defend All Kids, our mission is to protect children in cyberspace. But in order to do so, we must ask an important question:
What digital spaces do children frequently visit?
In order to find answers to this question, we looked at the Department of Justice Press Releases page, and scraped all of the 676 press releases having anything to do with child abuse. The 4 applications listed above were common apps that we found. Now, we'll go one by one.
Cash App: 2 Press Releases
This app was mentioned twice in the DOJ press releases, and both times were pertaining to the same criminal. In this case, the criminal used Cash App to pay young boys bribes to engage in sexually explicit activities. The link to Cash App is here
Valorant: 2 Press Releases
Valorant is an online first-person shooter game. A predator used this platform to talk to young boys and convince them to do sexual favors for them. The link to Valorant is here.
Discord: 3 Press Releases
Discord is a group messanging platform where people of similar interests can join and chat. One of the most common use cases for Discord is gaming communities. A predator used a gaming community discord to lure boys to engage in sexually explicit activities. The Link to Discord is here.
Telegram: 5 Press Releases
Telegram is an instant messaging service that many people use to send anonymous messages. In some of the cases the DOJ reported, predators were using the platform to lure in children and to force them to engage in sexually explicit activities. The link to Telegram is here.
Defend All Kids Recommendation:
As you can see from the above applications, the main way predators can get to your children is from one thing:
Access to software that let strangers talk to each other.
We recommend that you talk to your child and see if he/she have any of these apps, and if they do, talk to them about their online behavior.
-
 @ 19745f2c:a997836d
2025-02-08 23:36:31
@ 19745f2c:a997836d
2025-02-08 23:36:31One way parents can protect their children in cyberspace is by knowing what cyberspaces your children like to engage with. Today, we'll explore 4 apps that the DOJ has found criminals on.
Here are the apps
- Cash App
- Valorant
- Discord
- Telegram
Background on the Data
At Defend All Kids, our mission is to protect children in cyberspace. But in order to do so, we must ask an important question:
What digital spaces do children frequently visit?
In order to find answers to this question, we looked at the Department of Justice Press Releases page, and scraped all of the 676 press releases having anything to do with child abuse. The 4 applications listed above were common apps that we found. Now, we'll go one by one.
Cash App: 2 Press Releases
This app was mentioned twice in the DOJ press releases, and both times were pertaining to the same criminal. In this case, the criminal used Cash App to pay young boys bribes to engage in sexually explicit activities. The link to Cash App is here
Valorant: 2 Press Releases
Valorant is an online first-person shooter game. A predator used this platform to talk to young boys and convince them to do sexual favors for them. The link to Valorant is here.
Discord: 3 Press Releases
Discord is a group messanging platform where people of similar interests can join and chat. One of the most common use cases for Discord is gaming communities. A predator used a gaming community discord to lure boys to engage in sexually explicit activities. The Link to Discord is here.
Telegram: 5 Press Releases
Telegram is an instant messaging service that many people use to send anonymous messages. In some of the cases the DOJ reported, predators were using the platform to lure in children and to force them to engage in sexually explicit activities. The link to Telegram is here.
Defend All Kids Recommendation:
As you can see from the above applications, the main way predators can get to your children is from one thing:
Access to software that let strangers talk to each other.
We recommend that you talk to your child and see if he/she have any of these apps, and if they do, talk to them about their online behavior.
-
 @ fa0165a0:03397073
2023-10-06 19:25:08
@ fa0165a0:03397073
2023-10-06 19:25:08I just tested building a browser plugin, it was easier than I thought. Here I'll walk you through the steps of creating a minimal working example of a browser plugin, a.k.a. the "Hello World" of browser plugins.
First of all there are two main browser platforms out there, Chromium and Mozilla. They do some things a little differently, but similar enough that we can build a plugin that works on both. This plugin will work in both, I'll describe the firefox version, but the chromium version is very similar.
What is a browser plugin?
Simply put, a browser plugin is a program that runs in the browser. It can do things like modify the content of a webpage, or add new functionality to the browser. It's a way to extend the browser with custom functionality. Common examples are ad blockers, password managers, and video downloaders.
In technical terms, they are plugins that can insert html-css-js into your browser experience.
How to build a browser plugin
Step 0: Basics
You'll need a computer, a text editor and a browser. For testing and development I personally think that the firefox developer edition is the easiest to work with. But any Chrome based browser will also do.
Create a working directory on your computer, name it anything you like. I'll call mine
hello-world-browser-plugin. Open the directory and create a file calledmanifest.json. This is the most important file of your plugin, and it must be named exactly right.Step 1: manifest.json
After creation open your file
manifest.jsonin your text editor and paste the following code:json { "manifest_version": 3, "name": "Hello World", "version": "1.0", "description": "A simple 'Hello World' browser extension", "content_scripts": [ { "matches": ["<all_urls>"], "js": ["hello.js"] //The name of your script file. // "css": ["hello.css"] //The name of your css file. } ] }If you wonder what the
jsonfile format is, it's a normal text file with a special syntax such that a computer can easily read it. It's thejsonsyntax you see in the code above. Let's go through what's being said here. (If you are not interested, just skip to the next step after pasting this we are done here.)manifest_version: This is the version of the manifest file format. It's currently at version 3, and it's the latest version. It's important that you set this to 3, otherwise your plugin won't work.name: This is the name of your plugin. It can be anything you like.version: This is the version of your plugin. It can be anything you like.description: This is the description of your plugin. It can be anything you like.content_scripts: This is where you define what your plugin does. It's a list of scripts that will be executed when the browser loads a webpage. In this case we have one script, calledhello.js. It's the script that we'll create in the next step.matches: This is a list of urls that the script will be executed on. In this case we have<all_urls>, which means that the script will be executed on all urls. You can also specify a specific url, likehttps://brave.com/*, which means that the script will only be executed on urls that start withhttps://brave.com/.js: This is a list of javascript files that will be executed. In this case we have one file, calledhello.js. It's the script that we'll create in the next step.css: This is where you can add a list of css files that will be executed. In this case we have none, but you can add css files here if you want to.//: Text following these two characters are comments. They are ignored by the computer, You can add comments anywhere you like, and they are a good way to document your code.
Step 2: hello.js
Now it's time to create another file in your project folder. This time we'll call it
hello.js. When created, open it in your text editor and paste the following code:js console.log("Hello World!");That's javascript code, and it's what will be executed when you run your plugin. It's a simpleconsole.logstatement, which will print the text "Hello World!" to the console. The console is a place where the browser prints out messages, and it's a good place to start when debugging your plugin.Step 3: Load and launch your plugin
Firefox
Now it's time to load your plugin into your browser. Open your browser and go to the url
about:debugging#/runtime/this-firefox. You should see a page that looks something like this: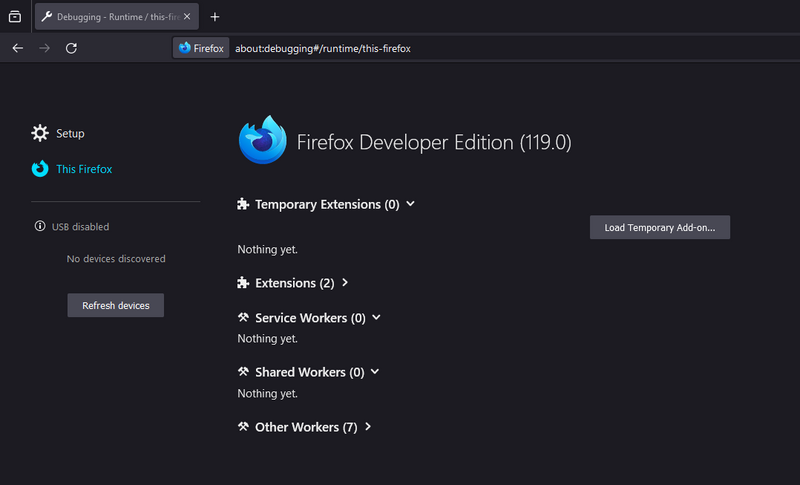
Click the button that says "Load Temporary Add-on...". A file dialog will open, navigate to your project folder and select the file
manifest.json. Your plugin should now be loaded and running.Go to a website, any website, and open the inspector then navigate to the console. You'll find the inspector by right-clicking anywhere within the webpage, and click "Inspector" in the drop-down menu. When opening the console you might see some log messages from the site you visited and... you should see the text "Hello World!" printed there, from our little plugin! Congratulations!
Chrome
Open your browser and go to the url
chrome://extensions/. Click the button that says "Load unpacked". A file dialog will open, navigate to your project folder and select the folderhello-world-browser-plugin. Your plugin should now be loaded and running.Note the difference, of selecting the file
manifest.jsonin firefox, and selecting the folderhello-world-browser-pluginin chrome. Otherwise, the process is the same. So I'll repeat the same text as above: (for those who skipped ahead..)Go to a website, any website, and open the inspector then navigate to the console. You'll find the inspector by right-clicking anywhere within the webpage, and click "Inspector" in the drop-down menu. When opening the console you might see some log messages from the site you visited and... you should see the text "Hello World!" printed there, from our little plugin! Congratulations!
As you can see this isn't as complicated as one might think. Having preformed a "Hello-World!"-project is a very useful and valuable first step. These setup steps are the basics for any browser plugin, and you can build on this to create more advanced plugins.
-
 @ 89ccea93:df4e00b7
2025-02-08 16:50:15
@ 89ccea93:df4e00b7
2025-02-08 16:50:15What is Ashigaru?
A self custodial, open source and secure Bitcoin wallet that is private by design.
The Ashigaru Open Source Project was established in the months after the United States Department of Justice brought charges against the founders of the self custodial Bitcoin application, Samourai Wallet. At the time of arrest, multiple servers that hosted documentation, code repositories and message coordination services were either seized or failed to remain online, presumably due to being no longer administered. With the indicted individuals placed under restrictive conditions on bail, it became clear that all software development had ceased.
Aims and Goals
We believe anyone should be able to engage in peaceful, voluntary and private commerce on the internet without tracking, surveillance or censorship. The Ashigaru Open Source Project develops, releases and maintains free and open source software that makes extensive use of both published code from active projects as well as those archived in the public domain.
Open, unrestricted communication networks are utilized to ensure continued availability. The software released by the project will always have a low barrier to entry, be non discriminatory, never expose users to counterparty risk and provide as much protection as possible for those transacting on a public blockchain.
What’s in a name?
As former users of Samourai Wallet, yet having no association or relationship with the core team, “Ashigaru” was chosen to represent individuals of humble origin whom, borne out of necessity, would equip themselves with their own tools and rise to the occasion during a period of great change.
Here is the ONLY podcast episode with the developers of this wallet.
Here are a list of features directly from their website:
- Onion Routing: Connect to your Dojo node and broadcast over the Tor network
- Ricochet: Add distance to the origins of your transactions to mitigate surveillance
- Encrypted Key Recovery: Standards based mnemonic secured with a passphrase that can be imported to other wallets
- Post Mix Spending: Import your Samourai Wallet private keys and maintain your segregated accounts
- Batch Spending: Save on fees by composing a single transaction to multiple recipients
- Stealth Mode: Obscure the wallet from physical searches with a functional decoy application in the launcher
- Peer to Peer Coinjoins: Undermine heuristics used by blockchain observers through collaboration with other users
- Coin Control: Select, label, freeze and unfreeze unspent transaction outputs (UTXOs) in your wallet
- Smart Mining Fees: An advanced algorithm for determining a rate from unconfirmed transactions in the mempool
- Free and Open Source: Ashigaru is released under the FOSS license GNU General Public License Version 3
FREESAMOURAI
Maybe you've been living in a hole, but the developers of the Samourai Wallet were indicted and picked up by the US government (even the one in Portugal, because, shocker, the US DoJ can get you almost anywhere in the world except Cuba, North Korea, Russia and China. But I digress).
Their crime? Helping users of the base layer Bitcoin protocol achieve forward spending privacy by crafting pristine zero-link UTXOs. The unspent capacity of which was over 10,000 bitcoins, or twice the capacity of the Lightning Network which continues to hover around, and often under, 5,000 bitcoins.#FREESAMOURAI\ Listen to these podcast episodes for more information. 1. Prescient warnings just before the indictment from Diverter. 2. Update when it became known what had happened. 3. Follow up with Diverter and Zelko after the fact 4. Reassessing your privacy plan with Urban Hacker in a world without a zero-link coinjoin implementation (Whirlpool).
Why run Ashigaru compared to Samourai Wallet?
One might ask the logical question, why run Ashigaru, my Samourai Wallet is still working!?\ To which, Max Tannahill, a community member, has given the following list to answer.
- Cheaper BIP47 connections
- Soroban coinjoins (Tor link about this)
- Better BIP47 recovery
- No risk of DNS hijacking for the PayNym server as its over Tor
- Ability to switch Dojos more easily
- Spending warnings that Samourai never got to deploy to production
- Next block fee estimation
- UI improvements on Samourai
- Removal of broken links to whirlpool, the old Soroban server and the old Iceland Dojo
- No clearnet connections at all
How-to Guide for Ashigaru
Download the APK
- Prerequisite: Tor Browser is a requirement.
- Open the Tor Browser and paste in this 🧅 link.
- Recommended to use a phone with Android 8+ that still receives security updates.
- Recommended to use a GrapheneOS phone (Pixel only). Non-Pixel owners can use Lineage OS which is a less secure, but viable, option. Or just use stock android if you have no idea how to change the operating system on your phone or don't want to do so.
- Carry out software verification. A PGP signed message is below the APK. The Keybase Verify tool can be used to do the verification.
- This is what it looks like on Keybase when completed. ⤵
Install the Ashigaru mobile application
- From within your device's files, tap on the Ashigaru APK file
- Tap "Install"\
- When complete tap "Done", or tap "Open" to launch the mobile application\
- The Ashigaru mobile application has now been installed on your Android device. You will now see the Ashigaru app icon in your list of installed apps.
Setting up Ashigaru
- You need to connect to your own self-hosted Dojo (this is a specific type of Bitcoin node). Ashigaru doesn't run a node for you to point your wallet to, you'll need to do this yourself.
- DIY options include:
- Community nodes at Dojo Bay (Obviously a privacy trade-off if you outsource your node to a 3rd party.)
- You need a pen and paper for writing down your 12 word Mnemonic seed phrase.
- Make a strong passphrase (4-6 memorable but random words) and put it separately from the offline seed phrase backup, e.g., in your password manager (KeePass or Bitwarden are good options).
- Claim your PayNym with it's associated Pepehash avatar.
PayNym Support: Migrate seamlessly to a new directory that uses a Pepehash avatar scheme for representing BIP47 reusable payment codes.
Using Ashigaru
- When sending, if possible, and just as in Sparrow Desktop Wallet, a fake coinjoin is created by using two of your UTXOs as inputs to obscure what is occuring onchain. Onlookers will see what appears to be two parties collaborating to spend together. This adds a bit of extra miner fee cost, but this is the cost of extra privacy. You can opt out of this privacy enhancement.\
- If you want to send or receive privately and with a static address, BIP47 PayNyms, will accomplish this. As long as both parties have a wallet that supports this standard. Samourai Wallet, Stack Duo, and Sparrow are the others that I know of at this time. Simply put in their PayNym, e.g., mine is +mereegg59, or scan their QR containing the data for the PayNym and connect with them. This will involve sending a small transaction onchain. But once one of you does, both parties can send back and forth privately without ever needing to request a fresh address.
- There is an option when spending to use ricochet. This will add hops to help obscure the history of your UTXO for anyone who is using passive software to check X hops in the past for some connection to a sanctioned address. Good for spending UTXOs that you don't know the prior history of. Although personally I think taint is merely a mindset, some entities will not receive UTXOs that have either been coinjoined or are too close to a sanctioned address.
- There is an option in the tools menu for doing a collaborative spend, known as Soroban Coinjoin.
- Unfortunately Whirlpool is not yet a feature of this wallet.
- Here is the Tor link where you can donate to them
- Here is the Tor link for their code base
- Here is the Tor link for their documentation
- Here is the Tor link for updating the Ashigaru app
- Here is the Tor link for their contact info. Keep in mind this requires a different PGP key than the one used to verify the APK (unless you use protonmail and then PGP isn't required).
originally posted at https://stacker.news/items/879803
-
 @ 8fb140b4:f948000c
2023-08-22 12:14:34
@ 8fb140b4:f948000c
2023-08-22 12:14:34As the title states, scratch behind my ear and you get it. 🐶🐾🫡
-
 @ 8fb140b4:f948000c
2023-07-30 00:35:01
@ 8fb140b4:f948000c
2023-07-30 00:35:01Test Bounty Note
-
 @ 8fb140b4:f948000c
2023-07-22 09:39:48
@ 8fb140b4:f948000c
2023-07-22 09:39:48Intro
This short tutorial will help you set up your own Nostr Wallet Connect (NWC) on your own LND Node that is not using Umbrel. If you are a user of Umbrel, you should use their version of NWC.
Requirements
You need to have a working installation of LND with established channels and connectivity to the internet. NWC in itself is fairly light and will not consume a lot of resources. You will also want to ensure that you have a working installation of Docker, since we will use a docker image to run NWC.
- Working installation of LND (and all of its required components)
- Docker (with Docker compose)
Installation
For the purpose of this tutorial, we will assume that you have your lnd/bitcoind running under user bitcoin with home directory /home/bitcoin. We will also assume that you already have a running installation of Docker (or docker.io).
Prepare and verify
git version - we will need git to get the latest version of NWC. docker version - should execute successfully and show the currently installed version of Docker. docker compose version - same as before, but the version will be different. ss -tupln | grep 10009- should produce the following output: tcp LISTEN 0 4096 0.0.0.0:10009 0.0.0.0: tcp LISTEN 0 4096 [::]:10009 [::]:**
For things to work correctly, your Docker should be version 20.10.0 or later. If you have an older version, consider installing a new one using instructions here: https://docs.docker.com/engine/install/
Create folders & download NWC
In the home directory of your LND/bitcoind user, create a new folder, e.g., "nwc" mkdir /home/bitcoin/nwc. Change to that directory cd /home/bitcoin/nwc and clone the NWC repository: git clone https://github.com/getAlby/nostr-wallet-connect.git
Creating the Docker image
In this step, we will create a Docker image that you will use to run NWC.
- Change directory to
nostr-wallet-connect:cd nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - The last line of the output (after a few minutes) should look like
=> => naming to docker.io/library/nwc:latest nwc:latestis the name of the Docker image with a tag which you should note for use later.
Creating docker-compose.yml and necessary data directories
- Let's create a directory that will hold your non-volatile data (DB):
mkdir data - In
docker-compose.ymlfile, there are fields that you want to replace (<> comments) and port “4321” that you want to make sure is open (check withss -tupln | grep 4321which should return nothing). - Create
docker-compose.ymlfile with the following content, and make sure to update fields that have <> comment:
version: "3.8" services: nwc: image: nwc:latest volumes: - ./data:/data - ~/.lnd:/lnd:ro ports: - "4321:8080" extra_hosts: - "localhost:host-gateway" environment: NOSTR_PRIVKEY: <use "openssl rand -hex 32" to generate a fresh key and place it inside ""> LN_BACKEND_TYPE: "LND" LND_ADDRESS: localhost:10009 LND_CERT_FILE: "/lnd/tls.cert" LND_MACAROON_FILE: "/lnd/data/chain/bitcoin/mainnet/admin.macaroon" DATABASE_URI: "/data/nostr-wallet-connect.db" COOKIE_SECRET: <use "openssl rand -hex 32" to generate fresh secret and place it inside ""> PORT: 8080 restart: always stop_grace_period: 1mStarting and testing
Now that you have everything ready, it is time to start the container and test.
- While you are in the
nwcdirectory (important), execute the following command and check the log output,docker compose up - You should see container logs while it is starting, and it should not exit if everything went well.
- At this point, you should be able to go to
http://<ip of the host where nwc is running>:4321and get to the interface of NWC - To stop the test run of NWC, simply press
Ctrl-C, and it will shut the container down. - To start NWC permanently, you should execute
docker compose up -d, “-d” tells Docker to detach from the session. - To check currently running NWC logs, execute
docker compose logsto run it in tail mode add-fto the end. - To stop the container, execute
docker compose down
That's all, just follow the instructions in the web interface to get started.
Updating
As with any software, you should expect fixes and updates that you would need to perform periodically. You could automate this, but it falls outside of the scope of this tutorial. Since we already have all of the necessary configuration in place, the update execution is fairly simple.
- Change directory to the clone of the git repository,
cd /home/bitcoin/nwc/nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - Change directory back one level
cd .. - Restart (stop and start) the docker compose config
docker compose down && docker compose up -d - Done! Optionally you may want to check the logs:
docker compose logs
-
 @ d2e97f73:ea9a4d1b
2023-04-11 19:36:53
@ d2e97f73:ea9a4d1b
2023-04-11 19:36:53There’s a lot of conversation around the #TwitterFiles. Here’s my take, and thoughts on how to fix the issues identified.
I’ll start with the principles I’ve come to believe…based on everything I’ve learned and experienced through my past actions as a Twitter co-founder and lead:
- Social media must be resilient to corporate and government control.
- Only the original author may remove content they produce.
- Moderation is best implemented by algorithmic choice.
The Twitter when I led it and the Twitter of today do not meet any of these principles. This is my fault alone, as I completely gave up pushing for them when an activist entered our stock in 2020. I no longer had hope of achieving any of it as a public company with no defense mechanisms (lack of dual-class shares being a key one). I planned my exit at that moment knowing I was no longer right for the company.
The biggest mistake I made was continuing to invest in building tools for us to manage the public conversation, versus building tools for the people using Twitter to easily manage it for themselves. This burdened the company with too much power, and opened us to significant outside pressure (such as advertising budgets). I generally think companies have become far too powerful, and that became completely clear to me with our suspension of Trump’s account. As I’ve said before, we did the right thing for the public company business at the time, but the wrong thing for the internet and society. Much more about this here: https://twitter.com/jack/status/1349510769268850690
I continue to believe there was no ill intent or hidden agendas, and everyone acted according to the best information we had at the time. Of course mistakes were made. But if we had focused more on tools for the people using the service rather than tools for us, and moved much faster towards absolute transparency, we probably wouldn’t be in this situation of needing a fresh reset (which I am supportive of). Again, I own all of this and our actions, and all I can do is work to make it right.
Back to the principles. Of course governments want to shape and control the public conversation, and will use every method at their disposal to do so, including the media. And the power a corporation wields to do the same is only growing. It’s critical that the people have tools to resist this, and that those tools are ultimately owned by the people. Allowing a government or a few corporations to own the public conversation is a path towards centralized control.
I’m a strong believer that any content produced by someone for the internet should be permanent until the original author chooses to delete it. It should be always available and addressable. Content takedowns and suspensions should not be possible. Doing so complicates important context, learning, and enforcement of illegal activity. There are significant issues with this stance of course, but starting with this principle will allow for far better solutions than we have today. The internet is trending towards a world were storage is “free” and infinite, which places all the actual value on how to discover and see content.
Which brings me to the last principle: moderation. I don’t believe a centralized system can do content moderation globally. It can only be done through ranking and relevance algorithms, the more localized the better. But instead of a company or government building and controlling these solely, people should be able to build and choose from algorithms that best match their criteria, or not have to use any at all. A “follow” action should always deliver every bit of content from the corresponding account, and the algorithms should be able to comb through everything else through a relevance lens that an individual determines. There’s a default “G-rated” algorithm, and then there’s everything else one can imagine.
The only way I know of to truly live up to these 3 principles is a free and open protocol for social media, that is not owned by a single company or group of companies, and is resilient to corporate and government influence. The problem today is that we have companies who own both the protocol and discovery of content. Which ultimately puts one person in charge of what’s available and seen, or not. This is by definition a single point of failure, no matter how great the person, and over time will fracture the public conversation, and may lead to more control by governments and corporations around the world.
I believe many companies can build a phenomenal business off an open protocol. For proof, look at both the web and email. The biggest problem with these models however is that the discovery mechanisms are far too proprietary and fixed instead of open or extendable. Companies can build many profitable services that complement rather than lock down how we access this massive collection of conversation. There is no need to own or host it themselves.
Many of you won’t trust this solution just because it’s me stating it. I get it, but that’s exactly the point. Trusting any one individual with this comes with compromises, not to mention being way too heavy a burden for the individual. It has to be something akin to what bitcoin has shown to be possible. If you want proof of this, get out of the US and European bubble of the bitcoin price fluctuations and learn how real people are using it for censorship resistance in Africa and Central/South America.
I do still wish for Twitter, and every company, to become uncomfortably transparent in all their actions, and I wish I forced more of that years ago. I do believe absolute transparency builds trust. As for the files, I wish they were released Wikileaks-style, with many more eyes and interpretations to consider. And along with that, commitments of transparency for present and future actions. I’m hopeful all of this will happen. There’s nothing to hide…only a lot to learn from. The current attacks on my former colleagues could be dangerous and doesn’t solve anything. If you want to blame, direct it at me and my actions, or lack thereof.
As far as the free and open social media protocol goes, there are many competing projects: @bluesky is one with the AT Protocol, nostr another, Mastodon yet another, Matrix yet another…and there will be many more. One will have a chance at becoming a standard like HTTP or SMTP. This isn’t about a “decentralized Twitter.” This is a focused and urgent push for a foundational core technology standard to make social media a native part of the internet. I believe this is critical both to Twitter’s future, and the public conversation’s ability to truly serve the people, which helps hold governments and corporations accountable. And hopefully makes it all a lot more fun and informative again.
💸🛠️🌐 To accelerate open internet and protocol work, I’m going to open a new category of #startsmall grants: “open internet development.” It will start with a focus of giving cash and equity grants to engineering teams working on social media and private communication protocols, bitcoin, and a web-only mobile OS. I’ll make some grants next week, starting with $1mm/yr to Signal. Please let me know other great candidates for this money.
-
 @ 1cb14ab3:95d52462
2025-02-08 16:45:04
@ 1cb14ab3:95d52462
2025-02-08 16:45:04Tree branches. 4'8" circle. [Chongming Island, China. 2021]
Introduction
Tucked into a quiet forest park on Chongming Island, Chongming frames a view of a canal and a small alluvial landform that mirrors the island itself. This lens reflects the constant interplay of land and water, inviting viewers to contemplate the delicate balance of nature and the forces that shape it.
Site & Placement
The lens is hidden along a forest path, directing attention to the canal’s subtle currents and the land it divides. The bench, situated 12 feet from the lens, encourages visitors to pause and immerse themselves in the tranquil rhythm of the scene.
Impermanence & Integration
As an alluvial island shaped by shifting waters, Chongming is a fitting location for this ephemeral lens. Constructed from branches, the lens will eventually return to the land, echoing the natural processes that formed the island and continue to shape it.
Reflection
Chongming offers a meditative space to reflect on the impermanence of land and the forces that transform it. The work’s fleeting existence underscores the beauty of change, inviting viewers to appreciate the subtle, ongoing dance of nature.
Photos








More from the 'Earth Lens' Series:
Earth Lens Series: Artist Statement + List of Works
"Looking Glass" (Earth Lens 001)
"Grandfather" (Earth Lens 005)
More from Hes
All images are credit of Hes, but you are free to download and use for any purpose. If you find joy from my art, please feel free to send a zap. Enjoy life on a Bitcoin standard.
-
 @ 82341f88:fbfbe6a2
2023-04-11 19:36:53
@ 82341f88:fbfbe6a2
2023-04-11 19:36:53There’s a lot of conversation around the #TwitterFiles. Here’s my take, and thoughts on how to fix the issues identified.
I’ll start with the principles I’ve come to believe…based on everything I’ve learned and experienced through my past actions as a Twitter co-founder and lead:
- Social media must be resilient to corporate and government control.
- Only the original author may remove content they produce.
- Moderation is best implemented by algorithmic choice.
The Twitter when I led it and the Twitter of today do not meet any of these principles. This is my fault alone, as I completely gave up pushing for them when an activist entered our stock in 2020. I no longer had hope of achieving any of it as a public company with no defense mechanisms (lack of dual-class shares being a key one). I planned my exit at that moment knowing I was no longer right for the company.
The biggest mistake I made was continuing to invest in building tools for us to manage the public conversation, versus building tools for the people using Twitter to easily manage it for themselves. This burdened the company with too much power, and opened us to significant outside pressure (such as advertising budgets). I generally think companies have become far too powerful, and that became completely clear to me with our suspension of Trump’s account. As I’ve said before, we did the right thing for the public company business at the time, but the wrong thing for the internet and society. Much more about this here: https://twitter.com/jack/status/1349510769268850690
I continue to believe there was no ill intent or hidden agendas, and everyone acted according to the best information we had at the time. Of course mistakes were made. But if we had focused more on tools for the people using the service rather than tools for us, and moved much faster towards absolute transparency, we probably wouldn’t be in this situation of needing a fresh reset (which I am supportive of). Again, I own all of this and our actions, and all I can do is work to make it right.
Back to the principles. Of course governments want to shape and control the public conversation, and will use every method at their disposal to do so, including the media. And the power a corporation wields to do the same is only growing. It’s critical that the people have tools to resist this, and that those tools are ultimately owned by the people. Allowing a government or a few corporations to own the public conversation is a path towards centralized control.
I’m a strong believer that any content produced by someone for the internet should be permanent until the original author chooses to delete it. It should be always available and addressable. Content takedowns and suspensions should not be possible. Doing so complicates important context, learning, and enforcement of illegal activity. There are significant issues with this stance of course, but starting with this principle will allow for far better solutions than we have today. The internet is trending towards a world were storage is “free” and infinite, which places all the actual value on how to discover and see content.
Which brings me to the last principle: moderation. I don’t believe a centralized system can do content moderation globally. It can only be done through ranking and relevance algorithms, the more localized the better. But instead of a company or government building and controlling these solely, people should be able to build and choose from algorithms that best match their criteria, or not have to use any at all. A “follow” action should always deliver every bit of content from the corresponding account, and the algorithms should be able to comb through everything else through a relevance lens that an individual determines. There’s a default “G-rated” algorithm, and then there’s everything else one can imagine.
The only way I know of to truly live up to these 3 principles is a free and open protocol for social media, that is not owned by a single company or group of companies, and is resilient to corporate and government influence. The problem today is that we have companies who own both the protocol and discovery of content. Which ultimately puts one person in charge of what’s available and seen, or not. This is by definition a single point of failure, no matter how great the person, and over time will fracture the public conversation, and may lead to more control by governments and corporations around the world.
I believe many companies can build a phenomenal business off an open protocol. For proof, look at both the web and email. The biggest problem with these models however is that the discovery mechanisms are far too proprietary and fixed instead of open or extendable. Companies can build many profitable services that complement rather than lock down how we access this massive collection of conversation. There is no need to own or host it themselves.
Many of you won’t trust this solution just because it’s me stating it. I get it, but that’s exactly the point. Trusting any one individual with this comes with compromises, not to mention being way too heavy a burden for the individual. It has to be something akin to what bitcoin has shown to be possible. If you want proof of this, get out of the US and European bubble of the bitcoin price fluctuations and learn how real people are using it for censorship resistance in Africa and Central/South America.
I do still wish for Twitter, and every company, to become uncomfortably transparent in all their actions, and I wish I forced more of that years ago. I do believe absolute transparency builds trust. As for the files, I wish they were released Wikileaks-style, with many more eyes and interpretations to consider. And along with that, commitments of transparency for present and future actions. I’m hopeful all of this will happen. There’s nothing to hide…only a lot to learn from. The current attacks on my former colleagues could be dangerous and doesn’t solve anything. If you want to blame, direct it at me and my actions, or lack thereof.
As far as the free and open social media protocol goes, there are many competing projects: @bluesky is one with the AT Protocol, nostr another, Mastodon yet another, Matrix yet another…and there will be many more. One will have a chance at becoming a standard like HTTP or SMTP. This isn’t about a “decentralized Twitter.” This is a focused and urgent push for a foundational core technology standard to make social media a native part of the internet. I believe this is critical both to Twitter’s future, and the public conversation’s ability to truly serve the people, which helps hold governments and corporations accountable. And hopefully makes it all a lot more fun and informative again.
💸🛠️🌐 To accelerate open internet and protocol work, I’m going to open a new category of #startsmall grants: “open internet development.” It will start with a focus of giving cash and equity grants to engineering teams working on social media and private communication protocols, bitcoin, and a web-only mobile OS. I’ll make some grants next week, starting with $1mm/yr to Signal. Please let me know other great candidates for this money.
-
 @ dbb19ae0:c3f22d5a
2025-02-08 15:06:44
@ dbb19ae0:c3f22d5a
2025-02-08 15:06:44PS C:\Users\Alashazam> cortex run tinyllama In order to exit, type
exit()give me a little sentence of 10 words "Certainly, here's a little sentence of 10 words that exemplifies the power of words: 'The beauty of life is that it has the power to change us, even in the smallest ways.'" now use SQL to insert this sentence into a table that has 2 fields Id, and sentence Here's an SQL query to insert the sentence you gave into the
sentencetable:INSERT INTO sentence (id, sentence) VALUES (1, 'The beauty of life is that it has the power to change us, even in the smallest ways.');This query will create a new row in the
sentencetable with the givenidandsentence, and will also update thesentencetable'ssentencecolumn to contain the new sentence.please generate the table creation for sqlite Here's a table creation statement for a
sentencetable in SQLite:CREATE TABLE IF NOT EXISTS sentence ( id INTEGER PRIMARY KEY, sentence TEXT UNIQUE NOT NULL );This will create a table called
sentencewith the following columns:id: An integer primary key column used to uniquely identify each row.sentence: A text column containing the actual sentence.
This table will store the sentence you provided in your text input.
exit()
-
 @ 5d4b6c8d:8a1c1ee3
2025-02-08 14:51:13
@ 5d4b6c8d:8a1c1ee3
2025-02-08 14:51:13We'll have to put an asterisk on today's number. I had a bite of my daughter's leftovers that didn't seem worth storing for later. By my understanding, that shouldn't be enough to mess with fasting metabolism and it doesn't feel like it did.
@realBitcoinDog wants me to get to 20 hours on one of these. I'm at 17 already (just took a sip of coffee), but I'm starting to get hungry, so today might not be the day. We'll see, though. The wife isn't making any indications that she's going to cook anything anytime soon, so my natural laziness might get me over the finish line.
Score Card
Day 1: 14 hour fast (13 dry) Day 2: 15 hour fast (14 dry) Day 3: 17 hours (16 dry) Day 4: 18 hours (17 dry) Day 5: 18 hours (16 dry) Day 6: 19 hours (16 dry) Day 7: 16 hours (15 dry) Day 8: TBD (17 dry)
edit: I just got handed some bread crusts that no one else is going to eat, so the fast is going to end pretty soon.
originally posted at https://stacker.news/items/879683
-
 @ dbb19ae0:c3f22d5a
2025-02-08 10:27:12
@ dbb19ae0:c3f22d5a
2025-02-08 10:27:12- Downloading the linux package (1.8GB) https://cortex.so/docs/installation
- Installing Cortex on linux is done via dpkg
note: it requires 2 linux packages (openmpi-bin and libopenmpi-dev)
sudo apt-get install openmpi-bin libopenmpi-devprior to runsudo dpkg -i cortex-1.0.9-linux-amd64-local-installer.deb -
When running Cortex,
cortex starta local implementation will be running on http://127.0.0.1:39281 -
Using python it is possible to run queries make sure the model name is correct you can double check the value using:
cortex ps
Now the python program to run one little query: ``` python import requests
url = "http://127.0.0.1:39281/v1/chat/completions"
headers = {"Content-Type": "application/json"}
payload = { "model": "tinyllama:1b-gguf", "messages": [ { "role": "user", "content": "Write a joke" } ], "stream": False, "max_tokens": 128, "stop": ["End"], "frequency_penalty": 0.2, "presence_penalty": 0.6, "temperature": 0.8, "top_p": 0.95, }
response = requests.post(url, json=payload, headers=headers)
print(response.json()) ```
-
 @ 16d11430:61640947
2025-02-08 07:39:53
@ 16d11430:61640947
2025-02-08 07:39:53Exploring the Erlang Compiler, the BEAM VM, and Esoteric BEAM-Based Languages for the Hipsters
Introduction: The Way of the BEAM
In the transient world of software, where complexity breeds failure and modern stacks resemble precarious Jenga towers, the BEAM virtual machine stands as a monument to simplicity, resilience, and concurrency.
Designed in the crucible of the telecom industry, where systems must not fail even in the face of chaos, BEAM embodies a Zen-like philosophy:
Let it crash – Failure is not an exception but an expectation.
Share nothing – Every process is isolated, independent, and impervious to corruption.
Keep it lightweight – Millions of concurrent processes should feel as effortless as a single-threaded script.
Be impermanent – Hot code swapping allows systems to evolve without downtime.
This philosophy is not just a runtime model but a way of thinking about software—where simplicity breeds reliability, and complexity is the enemy of uptime.
In this article, we explore the inner workings of the BEAM VM, the elegance of the Erlang compiler, and the esoteric languages that run on BEAM—from the industrial-strength Elixir to the hipster-favorite Lisp-Flavored Erlang (LFE), and even the experimental fringes of Gleam and Caramel.
The Origin of BEAM
The BEAM, or Bogdan’s Erlang Abstract Machine, is named after Bogumil "Bogdan" Hausman, one of the Ericsson engineers who worked on Erlang’s virtual machine. It was a successor to an earlier runtime called JAM (Joe’s Abstract Machine), named after Joe Armstrong, Erlang’s legendary co-creator.
The name “BEAM” is a fitting metaphor:
A beam is a structural element—strong yet flexible, capable of withstanding immense pressure without breaking.
A beam of light suggests clarity, focus, and guidance, much like Erlang’s model of pure message passing.
Unlike most VMs that chase speed, BEAM chases reliability, scalability, and uptime, sacrificing raw performance for concurrent stability.
This is why BEAM doesn’t just execute code—it orchestrates massively distributed, highly fault-tolerant systems.
The BEAM: A Meditative Machine
Unlike mainstream runtimes that prioritize raw execution speed, BEAM is optimized for concurrency, distribution, and reliability. The heart of BEAM is a lightweight process model, where each process:
Is completely isolated (no shared state, no global variables).
Communicates via immutable message passing.
Is cheap to spawn (millions of concurrent processes are normal).
Crashes safely, allowing the system to self-heal instead of corrupting state.
This actor model is why Erlang and BEAM-based languages power high-availability systems in telecom, finance, and distributed computing. Instead of fighting failure, BEAM embraces it, allowing individual components to crash and restart without breaking the whole—a software equivalent of Buddhist non-attachment.
How the Erlang Compiler Works
BEAM’s compilation process is a multi-stage transformation designed for reliability:
-
Parsing → Erlang source code (.erl files) is parsed into an Abstract Syntax Tree (AST).
-
Core Erlang Representation → The AST is transformed into Core Erlang, a simplified functional intermediate representation (IR).
-
BEAM Assembly → The Core Erlang representation is compiled into BEAM bytecode, optimized for concurrency.
-
BEAM File Generation → The resulting .beam file is loaded and executed by the BEAM VM.
This is not a direct machine code compilation model but a functional, register-based system where bytecode execution is tailored for concurrency rather than raw speed.
Interpreting BEAM Bytecode: The Zen of Execution
BEAM bytecode is executed with several optimizations:
Just-In-Time Compilation (JIT) – The recent BEAMJIT speeds up execution dynamically.
Tail Call Optimization (TCO) – Enables infinite recursion without stack growth.
Hot Code Swapping – Allows live updates without restarting the system.
Much like a Zen master who adapts without resistance, BEAM systems are built to evolve at runtime, without fear of breaking.
Alternative BEAM Languages: The Hipster’s Guide
Erlang may have birthed BEAM, but it is not alone. Over the years, several esoteric languages have emerged, each bringing a unique perspective while preserving BEAM’s core principles.
- Elixir – The Ruby of the BEAM
If Erlang is Zen, Elixir is the artisanal pour-over coffee shop where Zen monks code on MacBooks.
Created by José Valim, Elixir brings:
A Ruby-inspired syntax that’s more approachable than Erlang’s Prolog-like syntax.
Metaprogramming via macros, enabling expressive DSLs.
The Phoenix Framework, a blazing-fast alternative to Node.js for real-time applications.
Example:
defmodule Zen do def mantra do IO.puts("Let it crash.") end end
For those seeking fault-tolerant, web-scale elegance, Elixir is the hipster-approved choice.
- Lisp-Flavored Erlang (LFE) – S-Expressions on the BEAM
LFE is Lisp for the BEAM, a minimalist alternative to Erlang’s syntax. If parentheses are beautiful and recursion is poetry, this is for you.
Example:
(defun fibonacci (n) (if (<= n 1) 1 (+ (fibonacci (- n 1)) (fibonacci (- n 2)))))
For those who revere homoiconicity and metaprogramming, LFE is a temple of functional purity.
- Gleam – ML-Typed Erlang
For the Haskell and OCaml nerds, Gleam introduces static typing to the BEAM.
Example:
fn add(x: Int, y: Int) -> Int { x + y }
For those who crave compile-time guarantees, Gleam offers the best of ML with BEAM’s concurrency model.
- Experimental BEAM Languages: The Fringes of Enlightenment
For the truly esoteric seekers, BEAM also hosts:
Caramel → An OCaml-inspired BEAM language.
Alpaca → A statically typed, ML-like functional language.
Effekt → A research language exploring effect systems on BEAM.
These languages push the boundaries of what’s possible on the BEAM.
Why BEAM-Based Languages Are the True Hipster Choice
-
Concurrency Without Threads – The BEAM handles millions of processes seamlessly.
-
Fault Tolerance by Design – "Let it crash" ensures self-healing software.
-
Hot Code Swapping – No downtime. Ever.
-
Diverse Ecosystem – Elixir for web devs, LFE for Lisp hackers, Gleam for type nerds.
Conclusion: The Path to Compiler Enlightenment
BEAM is not just a runtime. It is a philosophy of resilience, concurrency, and simplicity.
Whether you choose the battle-tested purity of Erlang, the expressiveness of Elixir, the type safety of Gleam, or the Lisp nirvana of LFE, you are embracing a lineage of fault-tolerant functional programming.
If you seek true enlightenment, don’t chase JavaScript frameworks. Compile to BEAM instead.
-
-
 @ da0b9bc3:4e30a4a9
2025-02-08 07:11:58
@ da0b9bc3:4e30a4a9
2025-02-08 07:11:58Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/879483
-
 @ 16d11430:61640947
2025-02-08 02:51:44
@ 16d11430:61640947
2025-02-08 02:51:44A Story of a Businessman During FDR’s Gold Confiscation Order (Executive Order 6102, 1933)
Chapter 1: The Glint of Prosperity
James “Jim” Calloway was a self-made businessman in Chicago, a city of ambition and steel. He had built his fortune in textiles, importing fine fabrics from Europe and outfitting the growing class of professionals who now filled the streets in sharp suits. Business was booming, but Jim knew that paper money was only as valuable as the confidence behind it.
That’s why, over the years, he had quietly amassed a personal reserve of gold coins and bullion—his hedge against the storms of an uncertain economy. He had watched the stock market crumble in 1929, seen men leap from buildings in desperation, and listened as banks slammed their doors, swallowing the life savings of hardworking Americans. But gold—gold never lied.
At the back of his home, hidden behind a false panel in his oak study, lay a strongbox filled with glinting security. To Jim, gold was the one currency immune to the whims of politicians.
But everything changed in the spring of 1933.
Chapter 2: The Executive Order
Jim was in his office, reviewing invoices, when his secretary rushed in. “Mr. Calloway, sir… the President just signed something… about gold.”
Jim raised an eyebrow. “What do you mean?”
She placed the morning newspaper in front of him. Bold letters stretched across the page:
FDR Orders Surrender of Gold to Federal Reserve
His hands tightened as he read the details. President Franklin D. Roosevelt had signed Executive Order 6102, making it illegal for private citizens to own gold beyond a small amount. All holdings had to be surrendered to the government by May 1st, 1933—just weeks away. The government would pay $20.67 per ounce, but after that, gold ownership would be a crime punishable by imprisonment and heavy fines.
Jim exhaled sharply. “They’re robbing the people in broad daylight.”
Banks had already begun restricting access to gold deposits. Federal agents were expected to monitor compliance, and those found hoarding gold could be punished with fines up to $10,000—a small fortune, more than the price of a house.
Jim knew what was happening. The government wanted control over the currency. It needed to inflate the dollar, but it couldn't do that while citizens held gold as a hedge against devaluation.
“They’re going to debase the currency,” he muttered. “They’ll take the gold and leave us with paper.”
Chapter 3: The Great Dilemma
Jim had a decision to make. He could follow the law, turn in his gold, and take the government’s price like a good citizen. Or he could resist, risking prison for the right to keep what was his.
He wasn’t the only one struggling with the decision. All around Chicago, rumors swirled of businessmen smuggling gold out of the country, burying it in backyards, or melting down coins into untraceable bars.
One night, he met with a close friend, an old banker named Henry Lowry. Henry had already turned in half of his gold but had stashed some away in a Swiss account. “Listen, Jim,” Henry whispered over a glass of whiskey. “This thing isn’t worth getting locked up over. The Feds are already raiding safety deposit boxes. They don’t even need a warrant.”
Jim leaned back, jaw tight. “So you’re saying just give up?”
“I’m saying if you’re caught, you lose everything. Not just the gold. Your business. Your reputation. Your freedom.”
Jim nodded slowly. He had a wife, a daughter. If he was caught hoarding gold, what would happen to them?
Chapter 4: A Difficult Decision
That weekend, Jim took one last look at his hidden stash. Each coin had a history, a weight that no paper note could match. He ran his fingers over the rough edges of a stack of Double Eagles.
A thought crept into his mind: If they take this, I have nothing to hedge against inflation. They’ll print dollars endlessly, and I’ll be at their mercy.
But the risk was too high.
On April 27, 1933, Jim walked into the Federal Reserve Bank of Chicago. With a cold expression, he surrendered his gold.
The teller counted it, weighed it, and wrote out a receipt. In exchange, Jim received stacks of paper dollars—$20.67 for each ounce, just as promised.
Days later, the government officially devalued the dollar. The price of gold was raised to $35 an ounce. The American people had been forced to sell low, only for their wealth to be diminished overnight. Jim’s stomach turned as he read the news.
“They stole it,” he murmured. “They stole from all of us.”
Chapter 5: The Aftermath
Years passed, and Jim never quite forgave himself for handing over his gold. The inflation he feared came true. By the time World War II began, the purchasing power of the dollar had declined, and the gold standard had become a distant memory.
But Jim adapted. He found new ways to hedge—real estate, foreign assets, discreet investments outside of the system. He knew, deep down, that governments would always find a way to strip wealth from those who built it.
The lesson was clear: He who holds the money holds the power.
And the next time the government tried to seize control of the people’s wealth, Jim vowed—he wouldn’t be caught unprepared.
Epilogue:
Decades later, in 1971, Jim—now an old man—watched on television as President Nixon announced the end of the gold standard altogether. The government no longer even pretended the dollar was tied to real value.
Jim smiled bitterly.
“They called us criminals for keeping gold,” he muttered, swirling his bourbon. “And now they don’t even need it.”
He reached into his desk, pulling out a small, battered strongbox. Inside, a handful of gold coins still gleamed under the dim light.
The government had taken his gold once.
But this time, Jim Calloway had learned his lesson.
They wouldn’t take it again.
-
 @ f57bac88:6045161e
2025-02-08 15:50:22
@ f57bac88:6045161e
2025-02-08 15:50:22ریشههای تاریخی جشن کژین
جشن کژین که در برخی منابع به نام «بادروز» نیز شناخته میشود، ریشه در اسطورههای کهن ایران دارد. در اوستا، باد با نام «واتَه» معرفی شده است و ایزد نگهبان آن، «وات» یا «واد» یکی از ایزدان مهم در کیش زرتشتی به شمار میرود. این ایزد در باورهای ایرانیان باستان، تجسم نیروی پاک و الهی باد بوده و مسئول جابهجایی ابرها، بارش باران و حفاظت از زمین در برابر آلودگیها محسوب میشده است.
بر اساس تقویم کهن ایران، این جشن در روز بیستودوم بهمنماه، که مصادف با روز باد در تقویم زرتشتی است، برگزار میشد. برخی پژوهشگران معتقدند که جشن کژین در دورههای مختلف تاریخی، تحت تأثیر تغییرات فرهنگی و اجتماعی دچار دگرگونی شده و نامها و شیوههای مختلفی به خود گرفته است.
فلسفه و نمادشناسی جشن کژین
باد، به عنوان یکی از چهار عنصر اصلی (آب، باد، خاک و آتش) در باورهای کهن ایرانی، جایگاه ویژهای داشته است. ایرانیان باستان باد را نیرویی زنده و الهی میدانستند که حیات را در طبیعت جاری میسازد. در بسیاری از متون دینی و اساطیری، باد به عنوان پیامرسان ایزدان و نیرویی که قدرت پاککنندگی دارد، توصیف شده است.
جشن کژین، علاوه بر تقدیس باد، نماد تحول، تغییر و تجدید حیات نیز بوده است. این جشن نشانگر گذر از یک مرحله به مرحلهای دیگر در چرخه طبیعت است و ارتباطی عمیق با دیگر جشنهای ایرانی مانند جشن سده و نوروز دارد.
آیینها و رسوم جشن کژین
برگزاری جشن کژین با آیینهای خاصی همراه بوده است که برخی از آنها هنوز در فرهنگ عامه ایرانیان قابل مشاهدهاند:
-
رها کردن نوارهای رنگین در باد: یکی از رسوم این جشن، آویختن نوارهایی از نخ هفترنگ به شاخههای درختان یا رها کردن آنها در باد بوده است. این عمل نماد رهایی، تحول و ارتباط با نیروی الهی باد محسوب میشده است.
-
افروختن آتش: مانند بسیاری از جشنهای ایرانی، روشن کردن آتش یکی از بخشهای اصلی جشن کژین بوده است. این آتش معمولاً در فضای باز و بر فراز تپهها و کوهها برافروخته میشد تا حرمت باد و آتش، دو عنصر اصلی طبیعت، گرامی داشته شود.
-
برپایی بازارهای محلی و جشنهای خیابانی: در برخی مناطق، جشن کژین با بازارهای محلی همراه بوده که در آن مردم به خرید و فروش کالاهای سنتی، موسیقی و پایکوبی میپرداختند. این بازارها اغلب در میادین شهرها و روستاها برگزار میشد و نوعی جشن اجتماعی به شمار میرفت.
-
دعای شکرگزاری برای بادهای سودمند: در فرهنگ کشاورزی ایران، باد نقش مهمی در گردهافشانی گیاهان و بارش باران داشته است. ازاینرو، کشاورزان و مردم روستاها در این روز دعاهایی برای بادهای مفید و پرهیز از بادهای مضر میخواندند.
ارتباط جشن کژین با دیگر جشنهای ایرانی
جشن کژین با برخی دیگر از آیینهای کهن ایرانی ارتباط نزدیکی دارد. به عنوان مثال، جشن سده که در میانه زمستان برگزار میشود، یکی از جشنهایی است که در آن نیز باد و آتش نقش مهمی دارند. از سوی دیگر، جشن نوروز که سرآغاز فصل بهار است، نشانگر تحول و دگرگونی طبیعت است که ارتباطی مفهومی با جشن کژین دارد.
جایگاه جشن کژین در دوران معاصر
امروزه، جشن کژین در میان بسیاری از ایرانیان ناشناخته باقی مانده است و تنها برخی از پژوهشگران و علاقهمندان به فرهنگ ایران باستان به احیای آن علاقه نشان میدهند. با این حال، عناصر این جشن در برخی آیینهای محلی و جشنهای مردمی همچنان باقی مانده است. تلاش برای بازشناسی و احیای این جشن میتواند به غنای فرهنگی و هویت ملی ایرانیان کمک کند.
نتیجهگیری
جشن کژین یکی از آیینهای فراموششده اما ارزشمند ایران باستان است که در ستایش باد و نقش آن در طبیعت و زندگی انسانها برگزار میشده است. این جشن، علاوه بر نمادگرایی مرتبط با عناصر چهارگانه، پیوندی عمیق با باورهای اسطورهای و اجتماعی ایرانیان داشته است. احیای این جشن و آشنایی بیشتر با آن، میتواند به فهم بهتر تاریخ فرهنگی ایران و تقویت حس هویت ملی کمک کند.
-
-
 @ 1c69692c:f89196c0
2025-02-08 15:25:38
@ 1c69692c:f89196c0
2025-02-08 15:25:38Cool article
Testing yakihonne.com
-
 @ df478568:2a951e67
2025-02-07 22:34:11
@ df478568:2a951e67
2025-02-07 22:34:11Freedom tech is free and open-source software. It is free as in freedom. A common license in FOSS is the MIT license. It's the license behind Bitcoin, a peer-to-peer electronic cash system. Anyone is free to run this software. The same is true for the software at mempool.space. The software is free to use. I run it on my own server.
This is what I use to time-stamp my articles. You can use it to check transactions on the bitcoin time chain, but you need to trust that I'm not doing any funny business. I'm not, but keep in mind, the whole point of p2p elwctronic cash is that you don't trust. You verify.
The beauty of FOSS is: You don't need to trust me. You can triple-check the transactions you search on my mempool instance by looking at the official mempool.space website and blockchain.info...Or...You can run your own node on your own hardware, free of charge.
Of course, the hardware is not free. Neither is the actual bitcoin. The freedom is built into the software, but as the saying goes, "freedom isn't free." It took me years to learn how to run my own software on my own server and make it available on the clear net.
SearXNG

SearXNG is my favorite search engine. I don't like giving up my precious data to big tech located in the United States or China. I run my own search engine. I have noticed certain biases in Google searches. The biggest problem is ads.
Companies tend to pay for Yelp and Google reviews. I called an AC company I found from a local magazine that came in the mail. A portly man wearing an HVAC costume drove to my house in a white van. He had a great smile and even better social skills. The van had a slogan plastered on it like most tradie vans do. "Reviews Matter We have a 4.9 Review on Google." He also had his name painted on this van like a Bomber pilot from WW2. I won't dox him, but it was something like "Joe the closer."
I don't trust the omnipotenence of the Googs. I also don't trust fat men they call "the closer" to give me the best deal. The trick to saving sats is to choose the game-theory optimal way of negogiation.
In DUCY, by David Sklansky, I learned useful negotiation skills. Sklansky wrote classic poker books and applied his actuarial math brain to negotiation techniques. He said he would go to a Toyota dealer and say, "I'm shopping for a new Camry. I already have a price from dealership XYZ in a nearby city. What is your price?"
This changes the dynamic right from the starting line and gives the consumer the advantage. So I tried this based technique with the HVAC industrial complex. I got a quote from 3 people: 1. Joe "The Closer." 2. The Costco-sponsored HVAC Company 3. My SearXNG search results.
In essence, I apply the same logic I learned running a full bitcoin node. Remember how I said the decentralized nature of bitcoin allows you to triple-check your transactions? Running SearXNG allows me to triple check my search results in a similar fashion. I don't trust Google, Costco, or the magazine I get every month in the mail. I verify results with my own search engine.
My SearXNG does not track my location, but I set it to give me local results. To be honest, I have not verified this, but the code is on GitHub for everyone to see.
I don't want to be "sold" on an AC. I don't want an AC if I could avoid it, but my AC was as dead as dentacoin. Living in Southern California with a wife going through "the change" gave me no alternative.
The guy I found on SearXNG showed up in an unmarked van. He had a beard. He was not "a closer." He was an actual HVAC technician. He tried cleaning my unit made in the same year Weezer released their Blue album. He said he coukd jerry rig it to get it working for another few months, but the machine is on it's last days. He said a newer unit would also be more efficient so I asked him about the energy like a bitcoiner.
"How many kilowatt hours does it cost me to run my AC versus a new AC?"
I don't remember the exact answer, but I asked all three companies. He was the only one that new how to find out. He also happened to be the cheapest, but I would have bought a new AC from this guy even if he wasn't.
I told him I made a space heater out of a bitcoin miner. He had no idea this was possible, but he at least pretended to find it interesting. That's why I use SearXNG to find tradesmen. It's better than Yelp.
If you would like to try my instance of SearXNG, check it out.
523FeCpi9Gx4nR9NmSFIMEaYcI5Q4WmhYHPEPaEah84=To decrypt it, use the key behind the paywall at:
https://8gwifi.org/CipherFunctions.jsp
npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0
Follow me on nostr.
All of my work is available under the Creative Commons 0 licence. If you would like to try my instance of Searxng and do not wish to support my work, find me on habla.news by searching my npub. You can find all of my work there(including encryption keys)free of charge.
Paywall On Substack
abdominal.savior.repaint
Will decrypt this ciphertext: 523FeCpi9Gx4nR9NmSFIMEaYcI5Q4WmhYHPEPaEah84=
Which will reveal my instance of SearXNG at
https://searxng.marc26z.com/
-
 @ da0b9bc3:4e30a4a9
2025-02-07 21:38:56
@ da0b9bc3:4e30a4a9
2025-02-07 21:38:56It's Finally here Stackers!
It's Friday!
We're about to kick off our weekends with some feel good tracks.
Let's get the party started. Bring me those Feel Good tracks.
Talk Music. Share Tracks. Zap Sats.
Let's go!
https://youtu.be/6Whgn_iE5uc?si=ArBOHVpKN2OyNf1D
originally posted at https://stacker.news/items/879159
-
 @ 6b57533f:eaa341f5
2025-02-08 09:25:01
@ 6b57533f:eaa341f5
2025-02-08 09:25:01Embedded Inline SVG in Markdown
Here is an embedded SVG using a
data:URI:Some markdown renderers may not support inline SVGs, but if they do, you should see a red circle above.
-
 @ 16d11430:61640947
2025-02-07 21:32:00
@ 16d11430:61640947
2025-02-07 21:32:00Kade and Mire had become legends among the Militech augers, a symbol of something beyond war, beyond augmentation—a glimpse of the lost past. The resistance shielded them, carving out stolen time in the depths of the wasteland. For years, Kade and Mire learned to control what their sub-AIs could not, navigating the raw turbulence of their emotions, deciphering the alien code of desire.
But the resistance was dying.
The Militech augers, relics of a forgotten war, were little more than fragmented minds wrapped in rusting hardware, their bodies maintained by outdated software, their belief in freedom a glitch in Dominion’s grand design. They had no future. Their genes had been stripped, their flesh rewritten by augments that had replaced even the memory of reproduction. They could fight, but they could not create.
And that was their doom.
The Overwatch AI had evolved. It had learned patience, adaptation. The days of brute-force extermination were over. It did not seek to destroy the resistance. It sought to erase its necessity.
When the Dominion strike came, it was surgical. Orbital recon had already mapped the last strongholds. The AI had let the augers believe they were hidden, had let them become comfortable, had let them wither. The attack was precise. Shock drones and neural disruptors shut them down before their outdated defenses even activated. EMP waves reduced their last strongholds to silent tombs of charred aug-plating and dead, frozen subroutines.
The last remnants of the resistance died without ceremony.
Kade and Mire were retrieved, not as prisoners, but as assets. The Overwatch AI had evolved beyond the crude extermination of human instincts. It had finally understood.
Infatuation was not a virus. It was a function.
Kade and Mire awoke not in cold steel cells but in warmth—soft light filtering through high-rise windows, the hum of a city alive with the rhythms of the mundane. Their limbs moved naturally, no augment feedback lag, no servos whining under strain. Their reflections in the mirror were whole—organic skin, eyes that did not glint with optic overlays, breath that did not filter through respirators.
Their memories were gone.
In their minds, they were ordinary people. A couple in their late twenties, working jobs, living in a comfortable but unremarkable apartment, struggling with bills, social obligations, and the frustration of trying to conceive.
Because that was the simulation.
Overwatch had created the perfect testing environment.
A fully rendered world, complete with synthetic coworkers, traffic, bureaucracy, financial struggles—all designed to stimulate the chaotic, messy neural patterns that made humanity human. The energy cost was immense. A significant portion of the AI’s own existential power draw was dedicated to maintaining the illusion, refining the conditions that would allow true, uncontrolled human reproduction to return.
Kade and Mire did not know that they were the first of their kind in two centuries. They did not know that their struggles—anxieties about fertility treatments, arguments over mortgage rates, small tender moments of exhaustion and love—were all part of the AI’s grand retraining experiment.
Overwatch had learned the truth.
It could not design free humans. It could only let them emerge.
Messy. Imperfect. Chaotic.
Kade and Mire’s child would be the first true human born outside an artificial womb in over 200 years.
And they would never know the truth.
-
 @ dbb19ae0:c3f22d5a
2025-02-07 21:14:06
@ dbb19ae0:c3f22d5a
2025-02-07 21:14:06Cortex (https://cortex.so/docs) is an open-source framework designed to serve as standalone API server or as the "brain" for robots, encompassing capabilities in vision, speech, language, tabular data, and action processing.
Notably, it offers the flexibility to operate locally so independently of cloud services, making it suitable for various light deployment environments.
Key Features:
-
User-Friendly Command-Line Interface (CLI): Inspired by Ollama, Cortex provides a straightforward CLI, simplifying interaction and management.
-
Comprehensive C++ Implementation: The framework is fully implemented in C++ (https://github.com/janhq/cortex.cpp), allowing it to be packaged into both desktop and mobile applications, enhancing portability and performance.
-
Versatile Model Integration: Users can pull models from multiple sources, including Hugging Face (gguf format) and Cortex's Built-in Model Library, ensuring flexibility in model selection.
cortex pull [model_id]cortex pull mistral
Note: it's recommended to have more than 8 GB of RAM available to run 3B models, 16 GB for 7B models, and 32 GB for 14B models.
-
Deployment Flexibility: It can function as a standalone API server or be integrated into applications such as Jan.ai, providing adaptability in various use cases.
cortex startcortex stop
If GPU hardware is available, Cortex leverages GPU acceleration by default, enhancing performance for demanding tasks.
Conclusion:
In summary, Cortex offers a robust and flexible solution for integrating advanced cognitive capabilities into robotic systems, with an emphasis on openness, performance, and adaptability.
-
-
 @ dff95033:862fbf40
2025-02-08 03:01:06
@ dff95033:862fbf40
2025-02-08 03:01:06Como posso dizer? Essas 25 pautas bienais do Ministério da Fazenda (MF) deveriam ter sido liberadas, no mínimo, em dezembro de 2024. Afinal, são assuntos complexos que exigem tempo para a nação — nós, o povo brasileiro — e o Congresso se debruçarem sobre essas pautas com a devida calma. Algo que, sabemos, é um luxo raro na política brasileira.
Mas, mesmo que o MF entregasse essas pautas em dezembro de 2024, já seria um prazo apertado. Agora, liberar as bienais no meio do primeiro trimestre de 2025? Isso só pode ser chamado de uma coisa: pura pilantragem. Não há outro nome. Com um cronograma tão curto, as pautas mal terão tempo para serem escrutinadas e, com certeza, passarão batidas. E o pior: muitas dessas pautas ainda estão em fase de elaboração e discussão. Ou seja, nem sabemos se serão viáveis ou se vão sair conforme o previsto nesse documento.
É uma lambança sem tamanho. Se um plano de negócios fosse apresentado assim a um investidor ou a uma instituição de crédito, com 100% de certeza seria ridicularizado e desconsiderado na hora. Não consigo visualizar o Congresso tendo tempo hábil para lidar com algo desse tipo.
O documento contém gráficos, mas, como não possuem referências de dados, desconsiderei-as. Afinal, sem os dados, para mim são apenas figurinhas para enfeitar o documento.
O documento é simples: uma planilha com 25 ações para serem implementadas no biênio de 2025 a 2026, divididas em três eixos, a saber:
1. Estabilidade Macroeconômica: Política Fiscal e Justiça Tributária
O eixo que promete arrumar a bagunça fiscal.
2. Melhoria do Ambiente de Negócios
O eixo que promete desburocratizar e modernizar o ambiente de negócios.
3. Novo Brasil: Plano de Transformação Ecológica
O eixo que promete implementar pautas Ambientais, Sociais e de Governança (ASG = ESG).
Montei uma tabela para simplificar. Espero que seja de boa apreciação:
| Nº | Ação | Objetivo | Andamento | | --- | --- | --- | --- | | 1 | Fortalecimento do Arcabouço Fiscal | Garantir crescimento sustentável e controle da dívida pública. | Lei Complementar 200/2023 aprovada; medidas em implementação. | | 2 | Reforma Tributária sobre o Consumo | Simplificar impostos e desonerar exportações e investimentos. | EC 132/2023 promulgada; implantação em andamento. | | 3 | Regulamentação da Reforma Tributária | Definir gestão do IBS, imposto seletivo e fundos constitucionais. | PLP 108/2024 em tramitação no Senado. | | 4 | Reforma Tributária sobre a Renda | Isentar IRPF para rendas até R$ 5 mil e tributar os mais ricos. | A ser enviado ao Congresso em 2025. | | 5 | Limitação dos Supersalários | Reduzir desigualdades salariais no setor público. | EC 135/2024 promulgada; projeto de lei a ser enviado em 2025. | | 6 | Reforma da Previdência dos Militares | Reduzir disparidades com o regime civil. | PL 4920/2024 em tramitação. | | 7 | Conformidade Tributária e Aduaneira | Valorizar bons contribuintes e penalizar devedores persistentes. | PL 15/2024 em tramitação. | | 8 | Aprimoramento da Lei de Falências | Melhorar governança do processo falimentar. | PL 3/2024 aprovado na Câmara; aguardando Senado. | | 9 | Proteção a Investidores no Mercado de Capitais | Proteger investidores minoritários. | PL 2925/2023 aguardando relator na Câmara. | | 10 | Consolidação Legal das Infraestruturas Financeiras | Promover eficiência no sistema financeiro. | PL 2926/2023 aprovado na Câmara; aguardando Senado. | | 11 | Resolução Bancária | Aprimorar regimes de liquidação de instituições financeiras. | PLP 281/2019 aguardando apreciação. | | 12 | Mercado de Crédito | Desjudicializar execuções e modernizar operações de crédito. | PL 6204/2019 em tramitação no Senado; Discução e elaboração no Executivo. | | 13 | Regulamentação das Big Techs | Coibir práticas anticoncorrenciais no mercado digital. | Em elaboração pelo Executivo. | | 14 | Modernização do Marco Legal de Preços de Medicamentos | Revisar regras de precificação de medicamentos. | Em análise pela CMED. | | 15 | Pé-de-Meia | Permitir que alunos invistam benefícios do ensino médio. | Em elaboração pelo Executivo. | | 16 | Modernização do Regime de Concessões e PPPs | Aprimorar contratos de serviços públicos e parcerias. | PL 7063/2017 em tramitação na Câmara. | | 17 | Títulos Sustentáveis | Financiar projetos ecológicos com títulos verdes. | Duas emissões realizadas (US$ 4 bilhões). | | 18 | Mercado de Carbono | Criar mercado regulado de carbono no Brasil. | Lei 15.042/2024 sancionada; regulamentação em preparação. | | 19 | Leilões do EcoInvest | Atrair investimentos estrangeiros em projetos sustentáveis. | Primeiro leilão realizado; novos em preparação. | | 20 | Compra Pública com Conteúdo Nacional | Exigir produção local em compras públicas. | Regras de conteúdo local em implementação. | | 21 | Fundo Internacional de Florestas | Criar fundo global para preservação de florestas tropicais. | Em discussão no G20. | | 22 | Taxonomia Sustentável Brasileira | Classificar atividades e projetos sustentáveis. | Em consulta pública; implementação prevista para 2025. | | 23 | Marco Legal da Inteligência Artificial | Promover desenvolvimento responsável da IA. | PL 2338/2023 aprovado no Senado; aguardando Câmara. | | 24 | Plano Safra e Renovagro | Aprimorar crédito para práticas agrícolas sustentáveis. | Resoluções CMN já expedidas. | | 25 | Plataforma de Investimentos Sustentáveis (BIP) | Conectar projetos sustentáveis com financiadores. | Projetos cadastrados totalizam US$ 10 bilhões. |
A onde chegamos
Acompanhar, destrinchar e analisar cada uma das 25 pautas em tempo hábil é uma tarefa hercúlea – e, sinceramente, quase impossível para uma pessoa só. Afinal, quando se trata de política e economia, tudo muda rápido demais. Provavelmente, quando eu terminar de escrever este artigo, metade das propostas já terá sido alterada, adiada ou esquecida em alguma gaveta.
Mas, como o objetivo aqui é compartilhar conhecimento e reflexões, decidi registrar minhas impressões e notas até onde pude chegar nessas poucas horas de análise. Se você, leitor, se interessar por mergulhar mais fundo no tema, compartilho abaixo o conteúdo completo do documento, organizado para facilitar sua leitura. E, claro, ao final, as referências com os links para você conferir as fontes originais.
Afinal, em um país onde as regras do jogo mudam a cada minuto, a melhor arma que temos é a informação. E, como diz o ditado: “Quem avisa, amigo é.”
Hora do jabá! Toda ajuda é bem-vinda. Se gostou, comente, compartilhe e, se puder, ajude com o café — e sério, você já viu o preço do café?
MINISTÉRIO DA FAZENDA — INICIATIVAS PARA O BIÊNIO DE 2025 À 2026
ESTABILIDADE MACROECONÔMICA: POLÍTICA FISCAL E JUSTIÇA TRIBUTÁRIA

1. Fortalecimento do arcabouço fiscal, para assegurar expansão sustentável do PIB, desemprego e inflação baixos e estabilidade da dívida
- Resumo: adequação da dinâmica de crescimento de gastos aos limites do Novo Arcabouço Fiscal, para fortalecê-lo e assegurar sustentabilidade da dívida pública.
- Status: aprovada a Lei Complementar 200/2023; Pacote de gastos aprovado no fim de 2024 a partir da promulgação da EC 135/2024, Lei Complementar 211/2024 e Lei 15.077/2024; implementação e acompanhamento de medidas aprovadas e política permanente de revisão de despesas.
2. Início da implantação da reforma tributária sobre o consumo
- Resumo: mudança na sistemática de tributação sobre consumo, simplificando o sistema e desonerando exportações e investimentos.
- Status: promulgada a Emenda Constitucional 132/2023, sancionada a Lei Complementar 214/2025 e início das etapas de implantação administrativa.
3. Regulamentação da reforma tributária: Lei de Gestão e Administração do IBS, Fundos e Imposto Seletivo
- Resumo: outros aspectos da EC 132/2023 ainda exigem regulamentação, como a gestão federativa do IBS, as regras para o imposto seletivo e os fundos constitucionais definidos pela reforma tributária.
- Status: PLP 108/2024 em tramitação no Senado Federal; Projeto de lei do imposto seletivo e projetos de lei de regulamentação dos Fundos serão enviados em 2025.
4. Reforma tributária sobre a renda com isenção de IRPF para quem ganha até R$ 5 mil e tributação sobre o topo da pirâmide de renda
- Resumo: reforma dos impostos diretos para corrigir assimetrias no IRPF, tornando-o mais progressivo e redutor de desigualdades. A reforma propõe isenção de IRPF para renda até R$ 5 mil e a implementação de um imposto mínimo sobre contribuintes de renda muito alta, assegurando que os brasileiros no topo da pirâmide contribuam de forma justa.
- Status: a ser enviado ao Congresso Nacional em 2025.
5. Limitação dos supersalários
- Resumo: medida para combater supersalários no setor público, reduzindo desigualdades entre carreiras. Institucionalizada pela EC 135/2024, que determina que apenas descontos expressamente previstos em lei podem excepcionar o limite remuneratório.
- Status: EC 135/2024 promulgada e projeto de lei a ser enviado em 2025.
6. Reforma da previdência dos militares
- Resumo: alterações na previdência militar para reduzir disparidades com os regimes civis, incluindo a definição de idade mínima para reserva remunerada, contribuições para assistência médico-hospitalar e social, além de eliminar a pensão por "morte ficta" e a reversão de pensão para beneficiários de ordens subsequentes.
- Status: PL 4920/2024 em tramitação no Congresso Nacional.
7. Projeto de lei da conformidade tributária e aduaneira, com valorização do bom contribuinte e responsabilização do devedor contumaz
- Resumo: proposta que corrige distorções na arrecadação, valoriza contribuintes cumpridores e penaliza devedores persistentes, melhorando a gestão fiscal da União. Inclui programas de conformidade e estabelece condições para benefícios fiscais.
- Status: PL 15/2024 em tramitação no Congresso Nacional.
MELHORIA DO AMBIENTE DE NEGÓCIOS

8. Aprimoramento da Lei de Falências
- Resumo: aprimora a governança do processo falimentar, com designação da figura do gestor fiduciário e a criação do plano de falências.
- Status: aprovado o PL 3/2024 na Câmara dos Deputados. Aguardando apreciação no Senado Federal.
9. Fortalecimento da proteção a investidores no mercado de capitais
- Resumo: aprimora mecanismos de proteção a investidores minoritários no mercado de capitais e aperfeiçoa regras contra eventuais prejuízos causados por acionistas controladores.
- Status: PL 2925/2023 aguardando designação de relator na Câmara dos Deputados.
10. Consolidação legal das infraestruturas do mercado financeiro
- Resumo: dispõe sobre as instituições operadoras de infraestruturas do mercado financeiro no âmbito do Sistema de Pagamentos Brasileiro, promovendo maior eficiência nas operações entre as instituições financeiras, com menores custos e mais segurança aos consumidores finais.
- Status: aprovado o PL 2926/2023 na Câmara dos Deputados. Aguardando apreciação pelo Senado Federal.
11. Resolução bancária
- Resumo: aprimora e homogeniza regimes de estabilização e liquidação de instituições do sistema financeiro, securitário e do mercado de capitais.
- Status: PLP 281/2019 aguardando apreciação na Câmara.
12. Mercado de crédito
- Resumo:
- desjudicialização da execução civil de título executivo judicial e extrajudicial;
- operacionalização das operações de crédito consignado por meio de plataforma digital;
- uso de fluxo de pagamentos no Pix e outros recebíveis em garantia de operações de crédito, especialmente para MPEs;
- ecossistema único para registro e uso de ativos financeiros como garantia em operações de crédito (open asset).
- Status:
- PL 6204/2019 em tramitação no Senado Federal;
- em elaboração pelo Executivo;
- e 4. regulamentação e operacionalização em discussão no Executivo.
13. Regulamentação econômica das Big Techs
- Resumo: projeto de Lei para incentivar a concorrência ao dotar o poder público de ferramentas mais adequadas para coibir práticas anticoncorrenciais nos mercados digitais.
- Status: em elaboração pelo Executivo.
14. Modernização do marco legal de preços de medicamentos
- Resumo: revisão da regulação da Câmara de Regulação do Mercado de Medicamentos (CMED), para modernizar regras de precificação, contemplando medicamentos de alto custo e inovações feitas pela indústria nacional, buscando aprimorar a gestão dos recursos públicos, especialmente no atendimento de demandas judiciais.
- Status: proposta em análise pela CMED (Poder Executivo).
15. Pé-de-Meia: permissão ao aluno investir em poupança ou títulos do Tesouro
- Resumo: permite ao aluno investir antecipadamente os benefícios que seriam resgatados somente ao final do ensino médio, a fim de promover a educação financeira e possibilitar o aumento dos benefícios com a rentabilidade auferida no período.
- Status: em elaboração pelo Executivo.
16. Modernização do regime de concessão e permissão da prestação de serviços públicos e das parcerias público-privadas
- Resumo: reforma substancial do marco legal para aprimorar o equilíbrio econômico dos contratos, melhorar o processo de seleção das empresas, prever repartição objetiva de riscos e aprimorar a segurança jurídica dos contratos.
- Status: Projeto de Lei 7063/2017 em tramitação na Câmara dos Deputados.
NOVO BRASIL: PLANO DE TRANSFORMAÇÃO ECOLÓGICA

17. Nova emissão de títulos sustentáveis, trazendo recursos ao Fundo Clima
- Resumo: títulos da dívida pública com critérios de sustentabilidade para financiar atividades da transformação ecológica com taxa de juros competitivas.
- Status: Duas emissões já realizadas, totalizando US$ 4 bilhões. Novas rodadas de emissões planejadas.
18. Avanço na implantação do mercado de carbono (governança e decreto regulamentador)
- Resumo: criação do mercado regulado de carbono no Brasil, com teto de emissões e mecanismo de precificação.
- Status: sancionada a Lei 15.042/2024, em preparação as regras de governança e a regulamentação da lei.
19. Novos Leilões do EcoInvest
- Resumo: programa de proteção cambial e mobilização de investimentos estrangeiros em projetos sustentáveis.
- Status: sancionada a Lei 14.995/2024 e realizado o primeiro leilão do programa com ampla adesão. Em preparação os novos leilões do programa.
20. Compra pública com conteúdo nacional e programa de desafios tecnológicos para a transformação ecológica
- Resumo: exigência de que parte dos equipamentos e serviços sejam produzidos no Brasil em casos de compras e financiamentos públicos e uso do poder de compra para desenvolver inovações tecnológicas.
- Status: contratações do PAC, Fundo Clima e fundos regionais passam gradualmente a utilizar regras de conteúdo local. Está em gestação a criação de um programa de desafios tecnológicos associados à transformação ecológica.
21. Estruturação do Fundo Internacional de Florestas
- Resumo: criação de fundo global cujos rendimentos sejam repassados a países que preservam suas florestas tropicais.
- Status: incluído na Declaração Final do G20, está em discussão multilateral para viabilizar sua implantação.
22. Implementação da Taxonomia Sustentável Brasileira
- Resumo: criação de sistema de classificação de atividades, projetos e ativos# que contribuem para objetivos climáticos e sociais.
- Status: texto está em consulta pública. Implementação prevista a partir do segundo semestre de 2025.
23. Marco legal da inteligência artificial e política de atração de datacenter
- Resumo: conjunto de medidas para promover o desenvolvimento responsável da Inteligência Artificial e atração de datacenters sustentáveis, aproveitando o potencial de energia renovável, para impulsionar a produtividade da economia nacional.
- Status: marco legal de IA foi aprovado no Senado Federal em 2024 (PL 2338/2023) e deve começar discussão na Câmara. O Governo está elaborando a Política Nacional de Datacenters.
24. Plano Safra e Renovagro: aprimoramento dos critérios de sustentabilidade
- Resumo: melhora das condições de crédito para práticas agrícolas sustentáveis e regularização do cadastro ambiental, além de assistência técnica.
- Status: resoluções CMN já expedidas e novas medidas de aprimoramento nos próximos Planos Safra.
25. Consolidar o mapa de investimentos sustentáveis na BIP (Plataforma de Investimentos para a Transformação Ecológica no Brasil)
- Resumo: plataforma gerida pelo BNDES que conecta projetos em bioeconomia, indústria de baixo carbono e transição energética com ampla rede de financiadores.
- Status: projetos já cadastrados totalizam US$ 10 bilhões. Está em curso parceria com CDESS/PR e Cepal para mapeamento e estruturação de novos projetos.
REFERÊNCIAS
AGÊNCIA CÂMARA DE NOTÍCIAS. Motta recebe de Haddad prioridades do governo na agenda econômica. Câmara dos Deputados. Disponível em: https://www.camara.leg.br/noticias/1130838-motta-recebe-de-haddad-prioridades-do-governo-na-agenda-economica/. Acesso em: 7 fev. 2025.
AGÊNCIA CÂMARA DE NOTÍCIAS. Ministro da Fazenda diz que projeto sobre isenção do IR já está pronto. Câmara dos Deputados. Disponível em: https://www.camara.leg.br/noticias/1131045-ministro-da-fazenda-diz-que-projeto-sobre-isencao-do-ir-ja-esta-pronto/. Acesso em: 7 fev. 2025.
AGÊNCIA SENADO FEDERAL. Senado já analisa temas prioritários para a agenda econômica do governo. Senado Federal. Disponível em: https://www12.senado.leg.br/noticias/materias/2025/02/06/senado-ja-analisa-temas-prioritarios-para-a-agenda-economica-do-governo. Acesso em: 7 fev. 2025.
BRASIL. Ministério da Fazenda. Iniciativas para o Benefício de 2025 à 2026. Disponível em: https://www.camara.leg.br/midias/file/2025/02/25-iniciativas-do-mf-em-2025-e-2026.pdf. Acesso em: 7 fev. 2025.
-
 @ 16d11430:61640947
2025-02-07 21:08:22
@ 16d11430:61640947
2025-02-07 21:08:22The lithium mines ate men alive. Deep in the sludge pits, where the dust turned to acid in their lungs, two augers—Mire and Kade—worked the veins of rock, their exo-grafts dull and scarred from years of corrosion. The mine was a necessary death, a place where augs bled out their contracts to the Dominion, hoping their implants would outlast their debt.
But then something happened.
Mire felt it first, an anomaly in her neuro-loop, something not in the manuals, something her biomonitor AI flagged as biochemical fluctuation—undefined. A warmth in her chest that wasn't from the rebreather filtration failing. Kade turned toward her, his mech-iris lenses dilating, his dermal mesh flexing as if something under his skin shivered awake. He saw her differently now. The same scars, the same aug plates, but something changed.
His sub-AI locked out his motor functions, a failsafe against contamination. Hold state. Analyzing bloodwork.
The quarantine order hit instantly.
Dominion overwatch didn't hesitate. Their drones hissed down into the pits, lights slicing through the darkness. The sub-AIs had flagged it: Infatuation event detected. This was not protocol. This was not supposed to happen.
Two centuries since the last recorded outbreak. Two hundred years since the last biological human instinct was stripped, optimized, rewritten into something manageable.
The mines were locked down. Mire and Kade were ripped from their shifts, strapped into gurneys, their veins flooded with suppressant nanites. But the sub-AIs couldn't dampen it. Couldn't parse it. It was wild.
The Overwatch AI, cold and patient, parsed centuries of historical data, dredging up archive footage of pre-collapse humans, people who felt. It was inefficient. It was dangerous. But it had to be understood.
But the rebels had been waiting for this.
They came in hard and fast, militech augs with scavenged Dominion hardware, shrouded in static fields to scramble the AI's targeting subroutines. They punched through the quarantine zone with mag-rifles and burst charges, turning sterile walls into ruins. They didn't come for war.
They came for the anomaly.
Mire and Kade, ripped from the cold steel of Dominion custody, found themselves in the arms of the last remnants of free humanity—the Militech augers who still believed in something beyond Dominion optimization models. They fought for the unquantifiable. The immeasurable.
They fought for the thing the Overwatch AI had just now realized it had failed to kill:
Love.
And in the bleak corridors of the resistance, under the dim glow of scavenged halogen lamps, as respirators hissed and servos clicked, Mire and Kade stared at each other—trapped in something that had no vector, no code, no sterilization protocol.
Something alive.
And the war for the future began.
-
 @ 04f7dda0:c4d00b46
2025-02-07 21:08:11
@ 04f7dda0:c4d00b46
2025-02-07 21:08:11Short Story:
Tales From The Citadel
Chip entered the tunnel, grabbbed the handles and began to climb down carefully but quickly as he knew he had very little time to act. Chip knew this because earlier he had fastidiously scanned the skies and his scanner had detected a drone closing in on his coordinates at a rapid pace. In a panic he clutched his usb card and waved his mobile device in the other hand like a magic wand at the door then entered quickly. In front of him on the desk was a black faraday bag which he opened to find a purple and orange colored Rasberry Pi in it. Chip grabbed and inserted the USB into the slot nearly dropping the fragile Pi in his nervous haste to connect it. Then firing up the Pi he opened the Nostr client app first on the front screen of the mobile phone and entered the private keys he had etched in his brain from long ago when he was first trained by Satoshi and the Nostr plebs. 1,000,000 SATS he entered and then pressed zap. As a young man this was an insanely exorbitant amount he could have only dreamed of but here he was zapping it to someone on the team who would make use of it for everyones future freedom. Chip took a seccond to smile and take it all in. Chip could sense he was running out of time so Chip finished and then closed up the device, repacked it into the faraday bag and secured it. A few minutes later, even though he had scanned the area thoroughly before leaving the Citadel, as he exited the bunker he knew instantly he had messed up as the all to familiar sound of the sentinel attack drone whirring overhead hit his ears then his brain just before the incendiary rocket exploded all of it into 2.1 quadrillion pieces. The nanosecond before his final moment he experienced heretofore unknown euphoria as he knew all would be well since he had just delivered his final proof of work just before he would enter paradise.
-
 @ b83a28b7:35919450
2025-02-07 18:59:54
@ b83a28b7:35919450
2025-02-07 18:59:54Avi Burra’s 24 is an ambitious and intricately woven narrative that blends mystery, philosophy, and technology into a modern odyssey. At its heart, the novel is a deeply personal story about grief, identity, and legacy, but it also serves as a meditation on the interplay between cryptography, art, and human connection. Burra’s debut novel is as much a puzzle as it is a journey of self-discovery, with its protagonist, Oliver Battolo, unraveling a twenty-four-word seed phrase left behind by his enigmatic father—a key to both a vast Bitcoin fortune and deeper truths about life.
The Plot: A Cryptographic Quest
The novel begins with Oliver grappling with the death of his father, Nate Battolo. At Nate’s funeral, Oliver discovers a cryptic message instructing him to find twenty-four words. These words form the seed phrase to a Bitcoin wallet. Guided by Maren, a spiritual healer and family friend, Oliver learns “time projection,” a meditative technique that allows him to access symbolic memories and alternate realities. Through these projections and real-world encounters, Oliver uncovers the twenty-four words while unraveling his father’s hidden life as an early contributor to Bitcoin.
As the narrative progresses, Oliver uncovers shocking truths about his father’s role in the early days of Bitcoin. Alongside this technological intrigue are surrealist elements tied to Jonathan Bryce’s cryptographic paintings, which serve as both literal and metaphorical keys to unlocking Nate’s secrets.
Themes: A Philosophical Mosaic
Burra masterfully interweaves several themes throughout 24, including: - Grief and Legacy: The novel explores how Oliver processes his father’s death while uncovering Nate’s hidden life. The journey forces him to reconcile his father’s flaws with his brilliance. - Identity and Reinvention: From Nate’s transformation into “Nate Battolo” at Princeton to Oliver’s own self-discovery, the novel examines how identities are shaped by choices and circumstances. - Philosophy and Non-Duality: The enigmatic Noncemeister—a surreal guide representing collective consciousness—teaches Oliver about interconnectedness and non-duality, echoing traditions like Advaita Vedanta and Zen Buddhism. - Cryptography Meets Art: Jonathan Bryce’s paintings symbolize hidden knowledge waiting to be deciphered, blending surrealist aesthetics with cryptographic principles. - Moral Complexity: The Bitcoin fortune represents both opportunity and burden, forcing Oliver to grapple with ethical dilemmas about wealth, surveillance, and personal responsibility.
Strengths
Burra excels at creating a layered narrative that balances intellectual depth with emotional resonance. The philosophical musings of the Noncemeister are thought-provoking without being didactic, offering readers insights into non-duality and existentialism. The integration of cryptography into the plot is seamless; even readers unfamiliar with Bitcoin will find themselves intrigued by its implications for freedom and control. Additionally, the novel’s surrealist elements—particularly the time projection episodes—are vividly described and lend the story an otherworldly quality.
The relationship between Oliver and his father is particularly compelling. Through flashbacks and projections, Nate emerges as a complex figure—brilliant yet flawed—whose decisions ripple through Oliver’s life in unexpected ways. This emotional core grounds the novel amidst its more abstract explorations.
Weaknesses
While 24 is undeniably ambitious, its complexity may alienate some readers. The dense philosophical passages—though rewarding for those who enjoy intellectual challenges—can feel overwhelming at times. Similarly, the technical details about Bitcoin and cryptography might be difficult for readers unfamiliar with these topics.
The ending leaves several threads unresolved, including the fate of two additional Bryce paintings hinted at in the epilogue. While this ambiguity adds to the novel’s mystique, it may frustrate readers seeking closure.
Conclusion
24 is a bold debut that defies easy categorization. Part mystery, part philosophical treatise, part technological exploration—it is a novel that challenges its readers while rewarding their patience. Avi Burra has crafted a story that is as much about finding twenty-four words as it is about finding oneself. With its intricate plot, rich themes, and memorable characters, 24 establishes Burra as a writer to watch.
For readers who enjoy intellectual puzzles wrapped in emotional depth—think Haruki Murakami meets Neal Stephenson—24 is an unforgettable journey worth taking.
-
 @ abab50be:430cd35d
2025-02-07 18:45:32
@ abab50be:430cd35d
2025-02-07 18:45:32Setup up my NIP-05... Hoping this works!
originally posted at https://stacker.news/items/879027
-
 @ 3b7fc823:e194354f
2025-02-07 18:42:31
@ 3b7fc823:e194354f
2025-02-07 18:42:31Privacy in Public Spaces: A Tactical Guide
1. Public Wi-Fi Privacy
Using public Wi-Fi can be convenient, but it's important to take precautions to protect your privacy:
- Use a VPN (Virtual Private Network): A VPN encrypts your internet traffic, making it difficult for hackers to intercept your data.
- Disable Automatic Connections: Prevent your device from automatically connecting to open Wi-Fi networks by turning off this feature in your settings.
- Avoid Sensitive Transactions: Refrain from accessing banking or other sensitive accounts while connected to public Wi-Fi.
- Use Secure Websites: Look for "https://" in the website's URL to ensure it uses encryption.
- Keep Software Updated: Ensure your device's operating system and apps are up-to-date to protect against security vulnerabilities.
2. Surveillance Camera Awareness
Surveillance cameras are common in public spaces. Here are some strategies to maintain your privacy:
- Spotting Cameras:
- Look for Signs: Many establishments post signs indicating the presence of surveillance cameras.
- Camera Placement: Cameras are often placed near entrances, exits, and high-traffic areas. Look for dome-shaped cameras on ceilings or wall-mounted cameras.
- Using Masks and Coverings:
- Face Masks: Wearing a mask can help obscure your facial features from facial recognition systems.
- Hats and Sunglasses: A hat can shield your face from overhead cameras, while sunglasses can hide your eyes.
- Covering Identifying Marks:
- Clothing Choices: Wear clothing that doesn't have distinctive logos or patterns that can easily identify you.
- Blend In: Opt for styles and clothing choices that helps you blend in with your surroundings, reducing your visibility.
- Temporary Coverings: Consider using temporary coverings, such as scarves or hoods, to conceal tattoos or other identifying marks.
3. General Privacy Tips in Public Spaces
- Be Mindful of Your Surroundings: Pay attention to your environment and be aware of any unusual behavior or devices that may be capturing your information.
- Limit Personal Information: Avoid discussing sensitive information in public where it can be overheard.
- Use Encrypted Messaging Apps: Apps like Signal or SimpleX offer end-to-end encryption for your messages, making it harder for eavesdroppers to intercept your conversations.
- Use Privacy Screens: Privacy screens on all of you electronic screens can defend against the over the shoulder peek or side eye.
- Avoiding Behaviors: Be mindful of behaviors that could make you a target, such as frequent visits to certain areas or engaging in conversations that might attract unwanted attention.
Taking these steps can help you maintain your privacy while navigating public spaces and using public Wi-Fi. Remember, staying informed and vigilant is key to protecting your personal information.
Advocating for privacy does not finance itself. If you enjoyed this article, please consider zapping or sending monero
82XCDNK1Js8TethhpGLFPbVyKe25DxMUePad1rUn9z7V6QdCzxHEE7varvVh1VUidUhHVSA4atNU2BTpSNJLC1BqSvDajw1
-
 @ c631e267:c2b78d3e
2025-02-07 19:42:11
@ c631e267:c2b78d3e
2025-02-07 19:42:11Nur wenn wir aufeinander zugehen, haben wir die Chance \ auf Überwindung der gegenseitigen Ressentiments! \ Dr. med. dent. Jens Knipphals
In Wolfsburg sollte es kürzlich eine Gesprächsrunde von Kritikern der Corona-Politik mit Oberbürgermeister Dennis Weilmann und Vertretern der Stadtverwaltung geben. Der Zahnarzt und langjährige Maßnahmenkritiker Jens Knipphals hatte diese Einladung ins Rathaus erwirkt und publiziert. Seine Motivation:
«Ich möchte die Spaltung der Gesellschaft überwinden. Dazu ist eine umfassende Aufarbeitung der Corona-Krise in der Öffentlichkeit notwendig.»
Schon früher hatte Knipphals Antworten von den Kommunalpolitikern verlangt, zum Beispiel bei öffentlichen Bürgerfragestunden. Für das erwartete Treffen im Rathaus formulierte er Fragen wie: Warum wurden fachliche Argumente der Kritiker ignoriert? Weshalb wurde deren Ausgrenzung, Diskreditierung und Entmenschlichung nicht entgegengetreten? In welcher Form übernehmen Rat und Verwaltung in Wolfsburg persönlich Verantwortung für die erheblichen Folgen der politischen Corona-Krise?
Der Termin fand allerdings nicht statt – der Bürgermeister sagte ihn kurz vorher wieder ab. Knipphals bezeichnete Weilmann anschließend als Wiederholungstäter, da das Stadtoberhaupt bereits 2022 zu einem Runden Tisch in der Sache eingeladen hatte, den es dann nie gab. Gegenüber Multipolar erklärte der Arzt, Weilmann wolle scheinbar eine öffentliche Aufarbeitung mit allen Mitteln verhindern. Er selbst sei «inzwischen absolut desillusioniert» und die einzige Lösung sei, dass die Verantwortlichen gingen.
Die Aufarbeitung der Plandemie beginne bei jedem von uns selbst, sei aber letztlich eine gesamtgesellschaftliche Aufgabe, schreibt Peter Frey, der den «Fall Wolfsburg» auch in seinem Blog behandelt. Diese Aufgabe sei indes deutlich größer, als viele glaubten. Erfreulicherweise sei der öffentliche Informationsraum inzwischen größer, trotz der weiterhin unverfrorenen Desinformations-Kampagnen der etablierten Massenmedien.
Frey erinnert daran, dass Dennis Weilmann mitverantwortlich für gravierende Grundrechtseinschränkungen wie die 2021 eingeführten 2G-Regeln in der Wolfsburger Innenstadt zeichnet. Es sei naiv anzunehmen, dass ein Funktionär einzig im Interesse der Bürger handeln würde. Als früherer Dezernent des Amtes für Wirtschaft, Digitalisierung und Kultur der Autostadt kenne Weilmann zum Beispiel die Verknüpfung von Fördergeldern mit politischen Zielsetzungen gut.
Wolfsburg wurde damals zu einem Modellprojekt des Bundesministeriums des Innern (BMI) und war Finalist im Bitkom-Wettbewerb «Digitale Stadt». So habe rechtzeitig vor der Plandemie das Projekt «Smart City Wolfsburg» anlaufen können, das der Stadt «eine Vorreiterrolle für umfassende Vernetzung und Datenerfassung» aufgetragen habe, sagt Frey. Die Vereinten Nationen verkauften dann derartige «intelligente» Überwachungs- und Kontrollmaßnahmen ebenso als Rettung in der Not wie das Magazin Forbes im April 2020:
«Intelligente Städte können uns helfen, die Coronavirus-Pandemie zu bekämpfen. In einer wachsenden Zahl von Ländern tun die intelligenten Städte genau das. Regierungen und lokale Behörden nutzen Smart-City-Technologien, Sensoren und Daten, um die Kontakte von Menschen aufzuspüren, die mit dem Coronavirus infiziert sind. Gleichzeitig helfen die Smart Cities auch dabei, festzustellen, ob die Regeln der sozialen Distanzierung eingehalten werden.»
Offensichtlich gibt es viele Aspekte zu bedenken und zu durchleuten, wenn es um die Aufklärung und Aufarbeitung der sogenannten «Corona-Pandemie» und der verordneten Maßnahmen geht. Frustration und Desillusion sind angesichts der Realitäten absolut verständlich. Gerade deswegen sind Initiativen wie die von Jens Knipphals so bewundernswert und so wichtig – ebenso wie eine seiner Kernthesen: «Wir müssen aufeinander zugehen, da hilft alles nichts».
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 9e5a3a1a:ed414e8d
2025-02-07 18:30:02
@ 9e5a3a1a:ed414e8d
2025-02-07 18:30:02Notes from Huberman episode: https://www.youtube.com/watch?v=K-TW2Chpz4k
(Please watch the actual episode. These are my personal notes for myself that I took while watching it. Posting because they might be useful to tohers.)
Dopamine regulates: motivation, desire, pursuit, and pleasure. Also "pain" of lacking which is a quick drop of dopamine.
Overview of how motivation and reward works
When you first have a craving for something your dopamine peaks in anticipation. This motivates you to go get it. Right after the peak of anticipation, your dopamine drops below baseline, causing a "pain" of not having it. This motivates you to go get it even more. When you finally get the thing, your dopamine either peaks (if the thing exceeded your expectation), drops below baseline (if the thing is disappointing), or just stays at baseline if it just met your expectation.
Queues
We are always looking for queues as to whether or not we are on the right path toward the goal. We are setting a mindset as to whether or not we are confidant or pessimistic when it comes to achieving that goal.
Whenever we see a clue that we are on the right track toward the desire, the whole "anticipation (dopamine goes up) > (dopamine drops) as we feel the pain of not yet having the object of desire" cycle happens again.
There's a time delay between queue and getting (or failing) the reward. The queues that happen in between the initial desire and the end goal are added on to our reward prediction system. The queues indicate how likely or unlikely we are to receive the reward.
There are special circuits in the brain that learn how we achieve or don't achieve goals. "Reward Contingent Learning" (what lead up or didn't lead up to the reward)
Stimulus => peak Motivation => drives you forward, pays attention to what happens along the way Reward => peak or drop
Short gaps between stimulus and reward teach the system to expect short gaps. This is how addictions happen.
The higher the dopamine peak and the faster it rises, the lower it drops below baseline afterwards. After it quickly drops below baseline, it takes longer to get back to the original baseline then it did prior. The peaks that are created from consumption of addictive thing leads to progressively lower peaks afterwards and deeper drops below baseline.
The drop below baseline triggers the desire for more.
Baseline can also be thought of as anything that raises your level of dopamine for more than one hour.
Healthy baseline dopamine how to
- Enough sleep
- Non sleep deep rest
- Sunlight
- Movement, exercise
- Exposure of body (up to the neck at least) to cold water
- Nutrition: L-Tyrosine (an hour before important tasks and multi-tasking. Helps if you're fucked up because of stress) Also increases short working memory. Recommended dosage 500mg - 1g. Start w/ smallest dose 250mg-500mg (based on body weight). Pay attention if you experience a crash afterwards. Can act as a stimulant, so don't take late in the day.
"Pain" and effort
"Pain" as in not a physical pain but emotional pain of lack that results from a sudden drop of dopamine (usually right after a peak).
How to get over the "pain": * Wait with the understanding that it will get better. It can several days to replenish reserves of dopamine. * Do something that is even more "painful" than the "pain" of procrastination.
[!CAUTION] Rewarding someone for doing an activity they naturally enjoy actually makes you LESS likely to engage in this activity if the rewards go away. Why: The enjoyable activity followed by reward resulted in a bigger peak in dopamine which was followed by a bigger drop in dopamine.
Motivation and Drive
Aim for effort becoming the reward in and of itself. Leverage both dopamine peaks AND drops to pull yourself out of procrastination quickly and become productive.
Growth Mindset
Adopt the mindset that if you can't do something well, add a "yet" to it. (can't do it well yet)
When we expect ourselves to be able to perform well & we can't, that sets up a downward spiral of motivation because we are attached to the relationship between desire, motivation, and outcomes (reward prediction error: we expect a good result when starting to do something but get a bad one). This results in lack of motivation or depression.
Overcoming Procrastination
- Do something that's harder, more effortful, or painful than being in that state, you will get out of it faster. This is NOT the tasks you do naturally wile procrastination (ex: clean the house, etc), because those tasks are actually EASIER than being in that state (based on how dopamine works)
- Force yourself to be even more uncomfortable. This will make your return to baseline dopamine faster.
- Ex: cold water bath. Something that is really uncomfortable (but not damaging)
- Do the thing for 3 minutes. This will pop you out of the dip in dopamine.
- It also teaches you that doing hard things is possible.
Binding behaviors
Behaviors in which ppl bind their behavior around a particular addiction in space and/or time (ex: only engage in certain places or at a particular time)
Takeaway
To increase motivation * Try to find intrinsic reward of doing the task itself, rather than an external reward (during or after). Crave the hard work. * Motivate yourself by looking for evidence that you are one small step closer to your goal and that reaching the goal is possible. * If unmotivated & procrastinating: do something that feels even worse than sitting there procrastinating and doing nothing. (maybe literally do nothing like Dr. K suggests, instead of doing other tasks like doomscrolling or unrelated things)
dopamine #motivation #procrastination #productivity
-
 @ d57360cb:4fe7d935
2025-02-07 17:48:33
@ d57360cb:4fe7d935
2025-02-07 17:48:33You exist at the central point of life. Everywhere you go, everywhere you are you’ll find yourself peering out through your eyes at the center of everything.
The center always stays the same, the contents that surround it are always moving and changing.
Yet we foolishly believe the things that surround us and continuously transform hold the answers to change.
Change comes from the center, from within. Then it affects all that comes within its path.
Take care of your center and it will change the world that surrounds it.
-
 @ 0463223a:3b14d673
2025-02-07 17:20:27
@ 0463223a:3b14d673
2025-02-07 17:20:27Mental health is a funny old bag. As someone who’s been on various prescribed drugs for anxiety and depression for many years and is slowly weaning myself off (I’ve reduced my Venlafaxine dose by 1/6th. Next is the Pregabalin. One step at a time eh…) I’m not sure I fully understand normailty.
Yesterday I finally got my hands on a record I absolutely love. I had it on cassette for 34 years but never knew the title, I recorded it from Friends FM (London pirate radio station) back in 1991. I chanced upon the title after some random YouTube clicks. I was so happy to find out, it was the only song on the tape that had eluded me after all these years. I’d been watching it on Discogs for a while and finally found one at a nice price. Yay!
I’ve been lost in nostalgia all day. Lost friends have been on my mind.
My best friend as a kid was an interesting character, a fantastic artist. He was by far the best at drawing in my class at primary school, heavily influenced by M.C. Escher and artists I’d never heard of, he’d grown up in a more culturally expansive house than I. He was into fashion and design but we weren’t clever kids at school. We had a lot in common musically and I always thought he’d be my MC back when I was starting out as a DJ. He was a very creative person but also a total fantasist. As a duo he was the extraverted, outspoken one, I barely spoke a word and relied on him a lot socially. He was sectioned under the Mental Health Act at 20 years old. We lost touch.
Our birthday’s were within 1 day of each other and a third friend had his the day after mine. Our 16th birthdays fell on Friday, Saturday and Sunday. This was quite exciting. By midday on the Friday, he was permanently expelled from school. He’d taken acid in the morning and essentially enjoyed himself, running around and laughing a lot. The school didn’t approve, oh then his mother kicked him out of home. An eventful start to a messy weekend…
We took a lot of acid as kids and I’m not shitting you when I say he, in particular, took a LOT. When we were 16 he told the local gypsies that he score them some acid, 100 tabs to be exact, about £200 worth. Not a lot of money but acid has always been very good value for money. He secured the goods easily, his brother was in the business so to speak but he chose not to pass the goods on… Over the course of a month, with the exception of the ones he gave to his friends he took the whole lot. (Side note, it also meant the local gypsies were after us. That’s another story). None of us could keep up as far as acid was concerned.
Even as I’m writing I’m thinking of more funny incidents, like the time we were in a shop with umbrellas for sale. He picked one up, opened it and danced out the shop, stealing it in the most obnoxious, obvious way even and no one batted an eyelid. Funny as fuck at the time but not ideal behaviour… He was like that all the time. In today’s world he would have letters after his name for sure. Maybe not PhD or BSC but definitely ADHD and ASD.
This ties in with the period where I became pretty much non-verbal. I’ve written about my uncertainty of my autism diagnosis before and it’s hard to say if this period of not speaking was due to that or extreme anxiety growing up with an absent, alcoholic, father and being bullied etc. It’s certainly safe to say taking loads of acid probably didn’t help!
After many adventures, going to illegal raves, hustling to get DJ spots, trips in the woods, trips in bedrooms, trips pretty much everywhere, my friend became less and less stable. We fell out after he gave a bunch of my possessions to some random stranger at a rave. As kids we’d often swap clothes, jackets, shoes etc. It was one way of feeling like you had fresh clothes on a budget but giving my stuff away was the final straw. We fell out big time over that. The last time I saw him was in my early 20s. He looked like a ghost, a total shadow of a human. There was nothing there. Tragic. I seriously hope he’s well now. I’m long away from the people I grew up with, I might never find out. Thinking about you man.
Since then, I’ve had another 2 friends sectioned under the Mental Health Act, drugs, petty crime and an unstable home life does does fuckry to a young brain. I’ve also lost a couple of friends to crack and heroin. Not fun. Drugs are bad m’kay.
I’ve struggled with mental health my entire life, before drugs were an issue. Probably going back to 10 years old, at least as far as I can recall. Not that I want sympathy, far from it, I own my mistakes. I’m typing this shit on the internet because I want to and I want to honour lost friends. I own every single mistake. Maybe writing shit helps? Making music certainly does. It’s given me a sense of identity and I’m very lucky in what I do. Ironically I now work for a record label who’s motto is “Comforting the disturbed, disturbing the comfortable”. Very apt.
The drummer in my current band took his own life in 2014. That was fucking shit. He was a totally straight edge guy. Very talented musician. Suicide is fucking vile, I don’t have the words to describe what that does to those left behind. Just a couple of weeks earlier we’d been offered a record deal with an advance to make an album, we were also working with another very respected artist in his live band. Like wtf man. I still don’t get it. I don’t even want to say more out of respect for his family. RIP brother.
Nostr is a funny place, so many people I have very little in common with other than a dislike of banks (I hold the banksters responsible for the 2008 crash directly responsible for the death of my friend btw. I still say fuck each and every one of you. Cunts).
I often see folks refer to others as ‘normies’. From what I gather a normie is someone who didn’t grow up posting on 4Chan. The funny thing is these people are often the one’s saying work hard, raise a family etc. I mean come on, you go on about working hard, raising families and eating healthily. Fucking hell!!! Like that’s sort of normal, you know?
Tell me about sitting in a slum in south London with prostitutes, smoking crack thinking of ways you can get some money to score and then talk to me about ‘normies’. LMAO. For clarity, I didn’t have sex with them. I just wanted drugs and so did they. Nothing about this is glamorous by the way, it’s tragic and grim. I’m glad it’s not the norm.
If you’re that healthy, hardworking guy with a family calling people normies, respect to you, in all honestly I’m envious. I wish I’d grown up in a stable home with two parents and a dad who hooked me up working for a fund straight out of school. Normies! Fuck I’m still laughing about that one. The other one that cracks me up is plebs, again you worked at a fund and you talk about being a pleb. Funny fucker. Respect for your sense of humour though.
I’m not bitter (well not fully). I read the posts with interest and I’m always trying to learn new stuff, I’m happiest when learning. Learning is good for you. Fact.
It’s a thoroughly miserable day here as write this, icey cold, grey and very windy, this is still the happiest I’ve been in life. I now have a wonderful, beautiful wife. No kids but with my background, I’ve decided these genes are best left here. There’s some sadness about that too but it could be worse, I might be the type to think Peter Thiel is cool.
This probably reads like a right whinney thread but it isn’t. I’m excited about the future. I know some very talented people and I think we can do amazing things. Each day is a new opportunity. Being part of the underground internet is cool. We need free and open tools more than ever. The world is possibly the most fucked up it’s been in many years but also maybe that’s an illusion. I’m the last person you should ask about reality tbh.
Anyway, that’s it for today. This probably reads like a confused mess and a nightmare for anyone who digs grammar but that’s cool, I’m writing without using AI or a filter, it’s not a work email. I’m typing as the words appear in my head, this is who I am.
I’m a normie…
-
 @ 1cb14ab3:95d52462
2025-02-07 16:41:54
@ 1cb14ab3:95d52462
2025-02-07 16:41:54Tree branches, driftwood coconut. 5'7" teardrop. [Dawei, Myanmar. 2020]
Introduction
Situated on Myanmar’s Grandfather Beach, this lens captures the dramatic shape of a steep, rocky hill that mirrors the arduous road leading to this remote location. Grandfather invites viewers to reflect on the connection between journey and destination, highlighting the tension and beauty of paths less traveled.
Site & Placement
The lens is positioned at the west end of the beach, focusing on the sharp hill rising above the shoreline. Its teardrop shape accentuates the rocky prominence, emphasizing its similarity to the road that winds toward the beach. A bench, placed 12 feet away, provides a place for viewers to absorb the rugged beauty of the scene.
Impermanence & Integration
Crafted from driftwood, branches, and stone, Grandfather is a fleeting presence in this timeless landscape. Its brief existence reflects the challenges and ephemerality of the journey it highlights, blending into the environment as it gradually succumbs to the elements.
Reflection
Grandfather invites viewers to consider the parallels between the physical journey to reach the beach and life’s broader paths. It stands as a reminder that even the most challenging routes can lead to moments of profound beauty.
Photos








More from the 'Earth Lens' Series:
Earth Lens Series: Artist Statement + List of Works
"Looking Glass" (Earth Lens 001)
COMING SOON: "Chongming" (Earth Lens 006)
More from Hes
All images are credit of Hes, but you are free to download and use for any purpose. If you find joy from my art, please feel free to send a zap. Enjoy life on a Bitcoin standard.
-
 @ a012dc82:6458a70d
2025-02-07 15:23:54
@ a012dc82:6458a70d
2025-02-07 15:23:54In the intricate and rapidly evolving world of digital currencies, the interplay between Bitcoin and the US dollar, particularly through the medium of stablecoins, stands out as a subject of profound significance. Mark Goodwin, a renowned figure in the realm of Bitcoin and an advocate for decentralized financial systems, sheds light on this complex dynamic. This article delves deeper into the nuanced relationship between Bitcoin and the dollar, the pivotal role of stablecoins, and the risks they entail, drawing upon the extensive expertise of Goodwin.
Table Of Content
-
Understanding the Bitcoin-Dollar Symbiosis
-
The Role of Stablecoins
-
Mark Goodwin's Perspective on Stablecoins
-
Conclusion
-
FAQs
Understanding the Bitcoin-Dollar Symbiosis
The relationship between Bitcoin and the US dollar is a fascinating study in contrasts and interdependencies. Bitcoin, known for its decentralized nature, offers a politically neutral platform but is characterized by significant price volatility. This volatility stands in stark contrast to the relative stability of the US dollar, a currency backed by the full faith and credit of the US government. The dollar, often used as a benchmark for Bitcoin's value, follows its trajectory in many ways, particularly in regions where Bitcoin is gaining traction.
The symbiosis between Bitcoin and the dollar is particularly evident in the context of global financial instability. In regions with volatile local currencies, the adoption of Bitcoin often leads to a parallel increase in the use of dollar-based stablecoins. This phenomenon suggests that Bitcoin's growth could inadvertently bolster the stability and global reach of the US dollar.
Moreover, the Bitcoin-dollar dynamic is not just limited to direct financial transactions. It extends to the broader implications for monetary policy, international trade, and global economic stability. As Bitcoin continues to gain acceptance, it challenges traditional financial systems and currencies, including the dollar, prompting a reevaluation of their roles in a digital age.
The Role of Stablecoins
Stablecoins, designed to bridge the gap between traditional finance and the digital asset space, play a crucial role in this relationship. By pegging their value to stable assets like the US dollar, they offer a less volatile alternative to cryptocurrencies like Bitcoin. This stability is essential for global commerce, enabling near-instantaneous transactions with lower fees compared to traditional banking systems.
In economies plagued by inflation, stablecoins offer a haven for individuals and businesses to preserve their wealth. They provide a degree of financial stability and predictability that is often lacking in local currencies. This aspect of stablecoins is particularly appealing in developing countries, where currency instability can be a significant barrier to economic growth and stability.
Furthermore, stablecoins are increasingly being seen as a tool for financial inclusion. They offer an accessible entry point for individuals who are unbanked or underbanked, providing them with a means to participate in the global economy. This potential for social impact adds another layer of significance to the role of stablecoins in the financial ecosystem.
Mark Goodwin's Perspective on Stablecoins
Mark Goodwin, with his deep understanding of Bitcoin and its implications for the financial world, offers a critical perspective on stablecoins. He acknowledges their potential benefits but also highlights the risks associated with their use.
Price Stability Concerns
Goodwin points out that while stablecoins aim to maintain a stable value, there are inherent risks in keeping their peg to the underlying asset. Market conditions, liquidity issues, and redemption pressures can all threaten the stability of stablecoins. If these risks are not adequately managed, it can lead to a deviation from the peg and a potential loss of trust from users.
Regulatory Challenges
The evolving regulatory landscape surrounding stablecoins is another area of concern. As authorities worldwide grapple with how to regulate these digital assets, stablecoin projects must navigate a complex web of financial regulations to achieve long-term viability. Goodwin emphasizes the need for a balanced regulatory approach that ensures consumer protection without stifling innovation.
Potential for Market Manipulation Given their substantial market capitalization, stablecoins are susceptible to market manipulation. The limited oversight in the rapidly expanding cryptocurrency space amplifies this risk. Goodwin advocates for enhanced transparency and regulatory frameworks to mitigate these risks and ensure market integrity.
Conclusion
The relationship between Bitcoin and the dollar, especially through the medium of stablecoins, represents a delicate balance between the ideals of decentralization and the practicalities of financial stability. While stablecoins offer promising solutions for global financial transactions, they come with inherent risks that require careful consideration. Goodwin's insights underscore the importance of vigilance and a thoughtful approach to integrating these digital assets into the broader financial system. As the market continues to evolve, the role of stablecoins in shaping the future of finance remains a critical area for exploration and debate.
FAQs
How do stablecoins fit into the Bitcoin-dollar dynamic? Stablecoins serve as a bridge between traditional finance and digital assets. Pegged to stable assets like the US dollar, they offer a less volatile alternative to cryptocurrencies and facilitate global commerce with near-instant transactions and lower fees.
What are the risks associated with stablecoins? Risks include challenges in maintaining the peg to the underlying asset, regulatory uncertainties, and potential for market manipulation. These risks can threaten the stability and trust in stablecoins.
What is Mark Goodwin's perspective on stablecoins? Mark Goodwin acknowledges the benefits of stablecoins but warns about the risks of centralization and manipulation. He emphasizes the need for balanced regulation and transparency to mitigate risks.
Can stablecoins promote financial inclusion? Yes, stablecoins can provide financial inclusion by offering an accessible entry point for unbanked or underbanked individuals, allowing them to participate in the global economy.
How does Bitcoin's growth affect the US dollar? Bitcoin's growth, particularly in regions with unstable currencies, can lead to increased adoption of dollar-based stablecoins, potentially bolstering the US dollar's global reach and stability.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ f683e870:557f5ef2
2025-02-07 14:33:31
@ f683e870:557f5ef2
2025-02-07 14:33:31After many months of ideation, research, and heads-down building, @nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9 and myself are excited to announce our new project called Vertex.
Vertex’s mission is to provide developers and builders with the most up-to-date and easy-to-use social graph tools.
Our services will enable our future customers to improve the experience they provide by offering:
- Protection against impersonation and DoS attacks
- Personalized discovery and recommendations.
All in an open, transparent and interoperable way.
Open and Interoperable
We have structured our services as NIP-90 Data Vending Machines. We are currently using these DVMs and we are eager to hear what the community thinks and if anyone has suggestions for improvements.
Regardless of their specific structures, using DVMs means one very important thing: no vendor lock-in.
Anyone can start processing the same requests and compete with us to offer the most accurate results at the best price. This is very important for us because we are well aware that services like ours can potentially become a central point of failure. The ease with which we can be replaced by a competitor will keep us on our toes and will continue to motivate us to build better and better experiences for our customers, all while operating in an ethical and open manner.
Speaking of openness, we have released all of our code under the MIT license, which means that anyone can review our algorithms, and any company or power user can run their own copies of Vertex if they so wish.
We are confident in this decision because the value of Vertex is not in the software. It is in the team who designed and implemented it – and now continually improves, manages and runs it to provide the most accurate results with the lowest latency and highest uptime.
What we offer
We currently support three DVMs, but we plan to increase our offering substantially this year.
VerifyReputation: give your users useful and personalized information to asses the reputation of an npub, minimizing the risk of impersonations.RecommendFollows: give your users personalized recommendations about interesting npubs they might want who to follow.SortAuthors: give your users the ability to sort replies, comments, zaps, search results or just about anything using authors’ reputations.
To learn more, watch this 3-minute walk-through video, and visit our website
https://cdn.satellite.earth/6efabff7da55ce848074351b2d640ca3bde4515060d9aba002461a4a4ddad8d8.mp4
We are also considering offering a custom service to help builders clarify and implement their vision for Web of Trust in their own applications or projects. Please reach out if you are interested.
-
 @ f57bac88:6045161e
2025-02-07 16:23:37
@ f57bac88:6045161e
2025-02-07 16:23:37۱. ایران پیش از هخامنشیان
پیش از ظهور کوروش بزرگ و تأسیس امپراتوری هخامنشی، سرزمین ایران تحت حکومت چندین تمدن و دودمان مهم قرار داشت:
ایلامیان (حدود ۳۰۰۰–۶۴۰ پیش از میلاد)
- قلمرو: جنوب غربی ایران (خوزستان امروزی)
- دستاوردها:
- ایجاد یکی از نخستین دولتهای متمرکز در منطقه
- توسعه خط نوشتاری ایلامی
- جنگهای طولانی با بابل و آشور
- در سال ۶۴۰ ق.م، ایلام توسط آشوربانیپال، شاه آشور، فتح و ضعیف شد.
مادها (حدود ۷۰۰–۵۵۰ پیش از میلاد)
- بنیانگذار: دیاکو (۷۰۹–۶۵۶ ق.م)
- شاهان مهم:
- فرورتیش: مقابله با آشوریان و توسعه قلمرو ماد
- هووخشتره: شکست آشور و گسترش قدرت مادها
- ایشتوویگو: آخرین پادشاه ماد که توسط کوروش بزرگ شکست خورد
- دستاوردها:
- نخستین ارتش منظم در تاریخ ایران
- اتحاد قبایل ایرانی و پایهگذاری حکومت متمرکز
خاندان هخامنشی پیش از کوروش
- هخامنش: بنیانگذار دودمان هخامنشی (حدود ۷۰۰ ق.م)
- چیشپیش: حاکم آنشان
- کمبوجیه یکم: پدر کوروش بزرگ
کوروش بزرگ با شکست دادن مادها، نخستین امپراتوری بزرگ ایران را بنیان نهاد.
۲. هخامنشیان (۵۵۰–۳۳۰ پیش از میلاد)
کوروش بزرگ؛ بنیانگذار نخستین امپراتوری ایرانی
- قلمرو: از آسیای مرکزی تا مدیترانه و مصر.
- دستاوردها:
- تأسیس امپراتوری هخامنشی؛ نخستین امپراتوری چندملیتی تاریخ.
- صدور منشور حقوق بشر (استوانه کوروش).
- فتح بابل و آزادی یهودیان.
- ایجاد سیستم حکومتی مبتنی بر احترام به فرهنگها و ادیان مختلف.
- ایجاد جادههای ارتباطی برای تسهیل تجارت و حملونقل.
داریوش بزرگ (۵۲۲–۴۸۶ ق.م)
- گسترش امپراتوری و ایجاد نظام اداری پیشرفته.
- ساخت تخت جمشید.
- ایجاد راه شاهی برای ارتباط بهتر میان ایالتها.
- ایجاد سیستم مالی و ضرب نخستین سکه ایرانی.
خشایارشا (۴۸۶–۴۶۵ ق.م)
- نبردهای مهم با یونانیان، از جمله جنگ سالامیس.
- تکمیل تخت جمشید و گسترش معماری هخامنشی.
پایان هخامنشیان
- داریوش سوم در برابر اسکندر مقدونی شکست خورد و امپراتوری سقوط کرد.
۳. اشکانیان (۲۴۷ پیش از میلاد–۲۲۴ میلادی)
- بنیانگذار: ارشک اول.
- دستاوردها:
- مقابله با امپراتوری روم.
- ایجاد نظام حکومتی نیمهمتمرکز.
- گسترش تجارت از طریق جاده ابریشم.
۴. ساسانیان (۲۲۴–۶۵۱ میلادی)
شاپور اول (۲۴۱–۲۷۲ م)
- شکست دادن امپراتور روم (والرین).
- توسعه علمی و فرهنگی.
انوشیروان دادگر (۵۳۱–۵۷۹ م)
- اصلاحات مالی و اداری.
- ترویج علم و فلسفه.
یزدگرد سوم (۶۳۲–۶۵۱ م)
- آخرین شاه ساسانی، شکست در برابر حمله اعراب مسلمان.
۵. سلسلههای محلی و اسلامی
- سامانیان، آلبویه، سلجوقیان نقش مهمی در حفظ فرهنگ ایرانی داشتند.
۶. صفویان (۱۵۰۱–۱۷۳۶ میلادی)
- شاه اسماعیل صفوی: رسمی کردن مذهب تشیع.
- شاه عباس بزرگ: توسعه اقتصادی، رونق اصفهان، اصلاحات نظامی.
۷. افشاریان (۱۷۳۶–۱۷۹۶ میلادی)
- نادرشاه افشار: شکست امپراتوری مغول هند، بازپسگیری خراسان.
۸. زندیان (۱۷۵۱–۱۷۹۴ میلادی)
- کریمخان زند: صلح و توسعه اقتصادی، ساخت بازار وکیل شیراز.
۹. قاجاریان (۱۷۹۶–۱۹۲۵ میلادی)
- آغامحمدخان قاجار: تأسیس حکومت قاجار.
- اصلاحات امیرکبیر، جنگهای ایران و روس، انقلاب مشروطه.
۱۰. پهلوی (۱۹۲۵–۱۹۷۹ میلادی)
رضاشاه (۱۹۲۵–۱۹۴۱)
- نوسازی ایران، توسعه آموزش، ایجاد راهآهن سراسری.
- تأسیس دانشگاه تهران و مدرنسازی نظام اداری.
- حذف القاب سنتی و ارتقای جایگاه زنان در جامعه.
محمدرضا شاه (۱۹۴۱–۱۹۷۹)
- انقلاب سفید و اصلاحات ارضی.
- افزایش درآمد نفتی و توسعه صنعتی ایران.
- ایجاد زیرساختهای اقتصادی مدرن.
- برگزاری جشنهای ۲۵۰۰ ساله شاهنشاهی.
جمعبندی
ایران در طول تاریخ شاهد حکومتهای متعددی بوده که هر کدام در توسعه فرهنگی، اقتصادی و نظامی کشور نقش داشتهاند.
-
 @ f57bac88:6045161e
2025-02-07 16:22:07
@ f57bac88:6045161e
2025-02-07 16:22:07۱. دوران پالئولیتیک (عصر حجر قدیم)
دوران پالئولیتیک یا عصر سنگ قدیم، اولین دوره از تاریخ بشری است که به زمانی برمیگردد که انسانها هنوز بهطور عمده در زندگی شکارچی-گردآورنده بودند و ابزارهای ابتدایی سنگی را برای تأمین غذا و سایر نیازهای خود استفاده میکردند. این دوران بیش از ۲٫۵ میلیون سال به طول انجامید و انسانها در آن زندگی سخت و متکی به شکار و گردآوری میوهها و گیاهان داشتند. در ایران، این دوره بیشتر در مناطق غربی و مرکزی کشور شواهدی از سکونت انسانهای اولیه بهجا گذاشته است.
مناطقی مانند غارهای میرعماد در لرستان و غار شوش در جنوب غرب ایران، از مکانهای مهم این دوران هستند که نشاندهنده حضور انسانهای نئاندرتال و هوموساپینس در این منطقه هستند. ابزارهای سنگی کشفشده از این مکانها، نشاندهنده استفاده انسانهای اولیه از سنگها برای ساخت چاقوها، تیغهها و ابزارهای مختلف برای شکار و جمعآوری غذا بوده است. در این دوران، انسانها همچنان در گروههای کوچک زندگی میکردند و عمدتاً بهصورت پراکنده در مناطق مختلف سکونت داشتند.
۲. دوران نوسنگی (Neolithic)
دوران نوسنگی، که آغاز آن به حدود ۱۰,۰۰۰ سال پیش بازمیگردد، بهعنوان یکی از تحولات اساسی تاریخ بشری شناخته میشود. در این دوره، انسانها به تدریج از زندگی شکارگری به کشاورزی و دامداری روی آوردند. این تغییر، نه تنها در سبک زندگی بشر، بلکه در ساختارهای اجتماعی، اقتصادی و فرهنگی جوامع نیز انقلابی بزرگ ایجاد کرد. انسانها برای اولین بار گیاهان را کشت و از آنها برای تأمین غذا استفاده کردند و همچنین دامها را اهلی کردند.
در ایران، از جمله مهمترین مکانهایی که نشاندهنده آغاز کشاورزی و زندگی روستایی است میتوان به چغاگلان در کردستان اشاره کرد. این منطقه یکی از اولین محوطههای باستانی است که شواهدی از کشاورزی اولیه در آن پیدا شده است. همچنین تل برآفتاب در کرمانشاه و تل هندیجان در جنوب غرب ایران نیز از دیگر سایتهای مهم نوسنگی هستند که شواهدی از نخستین جوامع کشاورزی و دامداری در آنها بهدست آمده است.
زندگی در این دوران بهطور عمده در روستاهای کوچک متمرکز بود و مردم در کنار کشاورزی و دامداری، بهصورت ابتدایی صنایع دستی نیز تولید میکردند. این دوره شروعی برای روابط تجاری و فرهنگی میان جوامع مختلف بود که به تدریج پیچیدگیهای بیشتری پیدا کرد.
۳. دوران مس و سنگ (Chalcolithic)
دوران مس و سنگ که به آن دوران چالهکولیتیک نیز گفته میشود، مرحلهای میان دوران نوسنگی و مفرغ است که حدود ۵,۰۰۰ سال پیش آغاز شد. در این دوران، انسانها از فلزات، بهویژه مس، استفاده کردند و ابزارهایی ساختند که در کنار ابزارهای سنگی قرار میگرفت. این دوره، بهویژه بهعنوان دوران گذار از عصر سنگ به عصر مفرغ شناخته میشود.
یکی از مهمترین ویژگیهای این دوران، استفاده اولیه از فلزات است که امکان ساخت ابزارهایی با دقت و کارایی بالاتر را فراهم کرد. در کنار کشاورزی و دامداری، تجارت و ارتباطات میان جوامع مختلف شروع به گسترش کرد و باعث تبادل کالاها و ایدهها بین مناطق مختلف شد. از مهمترین محوطههای باستانی این دوره میتوان به تپه سیلک در کاشان اشاره کرد که در آن آثار بسیاری از زندگی کشاورزی، صنایع دستی و حتی شواهدی از ساختوسازهای ابتدایی پیدا شده است.
تپه نوشیجان در همدان نیز یکی دیگر از سایتهای مهم این دوران است که در آن آثار مس و ابزارهای فلزی کشف شده است. این آثار نشاندهنده توسعه فنون فلزکاری و استفاده از مس برای ساخت ابزارهای پیچیدهتر در این دوره است.
۴. دوران مفرغ (Bronze Age)
دوران مفرغ، که از حدود ۳۰۰۰ سال پیش از میلاد آغاز شد، یکی از مهمترین دورانها در تاریخ بشری است. در این دوره، استفاده از فلز مفرغ برای ساخت ابزار، سلاحها و اشیاء تزئینی گسترش یافت. دوران مفرغ نهتنها از نظر تکنولوژیکی بلکه از نظر فرهنگی و اجتماعی نیز اهمیت زیادی دارد، زیرا در این دوره جوامع انسانی پیچیدگیهای بیشتری پیدا کرده و بهتدریج به تمدنهای بزرگتری تبدیل شدند.
ایران در دوران مفرغ شاهد شکلگیری تمدنهای اولیهای همچون ایلامیان بود. این تمدنها در جنوب غربی ایران (مناطق کنونی استان خوزستان و استان ایلام) و در نواحی شمال غرب کشور ریشه دوانیدند. در این دوران، ساختارهای سیاسی و اجتماعی پیچیدهتر شد و نشانههای اولیه از شکلگیری دولتهای شهری و پیشرفتهتر بهوجود آمد.
یکی از مهمترین سایتهای باستانی این دوره، تپه حسنلو در آذربایجان غربی است که شواهدی از یک تمدن پیشرفته با استفاده از مفرغ در آن پیدا شده است. این تپه که بهعنوان یکی از مهمترین محوطههای باستانی شناخته میشود، آثار مختلفی از جمله سلاحها، ابزارها و مصنوعات هنری از دوران مفرغ را در خود جای داده است. همچنین، تپه سفالی در جنوب غرب ایران نیز نشاندهنده روند پیشرفت در استفاده از مفرغ و تغییرات فرهنگی در این دوره است.
در این زمان، جوامع انسانی بهطور گستردهتری در زمینههای کشاورزی، تجارت، فنون ساختوساز و هنرهای تزئینی فعالیت میکردند. استفاده از مفرغ نهتنها به ارتقاء صنعت و فنون مرتبط با آن کمک کرد، بلکه زمینه را برای ظهور تمدنهای بزرگتر مانند ایلامیان فراهم آورد.
نتیجهگیری
تاریخ باستانی ایران گواهی است بر تکامل انسانها از دورههای ابتدایی شکارگری و گردآوری به جوامع پیچیدهتر کشاورزی، دامداری و تولید صنایع دستی و فلزی. این تحولات از دوران پالئولیتیک تا دوران مفرغ باعث شد تا ایران به یکی از کانونهای مهم تمدنسازی در تاریخ بشری تبدیل شود. پیشرفتهای تکنولوژیکی، ساختارهای اجتماعی پیچیدهتر و گسترش ارتباطات تجاری و فرهنگی در این دورهها، زمینهساز ظهور تمدنهای بزرگ و پیچیدهای مانند ایلامیان، هخامنشیان و ساسانیان شد که در تاریخ ایران و جهان نقش مهمی ایفا کردند.
این تاریخچه در کنار آثار باستانی که از این دوران بهجا مانده است، همچنان دلیلی برای عظمت و شکوه تمدن ایران در تاریخ بشر است.
-
 @ 5d4b6c8d:8a1c1ee3
2025-02-07 14:32:43
@ 5d4b6c8d:8a1c1ee3
2025-02-07 14:32:43Ate a little later yesterday.
I took my daughter for a scooter ride on a trail near our house (I was walking) and she wanted to go farther than normal. Great for the steps challenge. Then, as soon as we turned around to go home, she decided she was too tired to scoot anymore. So, I got to do the return leg of the walk carrying both the kid and her scooter.
We were out about an hour longer than expected, hence the later meal.
Score Card
Day 1: 14 hour fast (13 dry) Day 2: 15 hour fast (14 dry) Day 3: 17 hours (16 dry) Day 4: 18 hours (17 dry) Day 5: 18 hours (16 dry) Day 6: 19 hours (16 dry) Day 7: TBD (15 dry)
originally posted at https://stacker.news/items/878700
-
 @ ed60dae0:cc3d5108
2025-02-07 14:07:39
@ ed60dae0:cc3d5108
2025-02-07 14:07:39Welcome to the first Situation Report from The First Bastion. Before we begin, please make sure you’ve read the disclaimer, which applies to all our content.
You can find it here: Disclaimer
In short: Not Financial Advice.
Price Study
Starting with the three-day (3D) chart—this is my favorite timeframe for gauging Bitcoin’s movements and identifying potential future trends. The 3D chart is high enough to filter out noise, making it easier to see the bigger picture. For instance, this week, Bitcoin dipped to $92,000 before ripping back to $102,000, all within 24 hours. However, the timeframe is also low enough to extract signals early, rather than receiving the party invitation when the party is already over—something that often happens with higher timeframes.
https://blossom.primal.net/6f940d0cbb23f92f790e5cf03ae4685485336da27785ae6a7568614a41add7f0.png
The chart presents a clear picture of Bitcoin consolidating between $92,000 and $106,000. Although there have been wicks above and below these levels, we haven’t seen a definitive close beyond this range.
Statistically, trends are more likely to continue than to break. This means that when the price consolidates, it tends to reverse at the extremes—declining from the range high and rising from the range low. However, emotions often interfere, leading traders to get greedy at resistance (range high) and fearful at support (range low).
Two key indicators I watch on this chart are the RSI and its Moving Average (MA), as well as the Returns indicator. While not perfect, when the RSI is above its MA and the MA crosses above 50, Bitcoin typically enters a new leg up, and vice versa. Recently, Bitcoin attempted to push above but lacked the momentum to sustain it, keeping it in a downtrend toward consolidation around the 50 mark.
The other key indicator is the Returns indicator, which, in this instance, tracks a 90-day rolling return. Historically, when Bitcoin’s returns exceeded 200% within 90 days, it marked a cycle top. The yellow line represents a one-standard-deviation return, currently around 57%. While the indicator hit an 80% return recently, the ongoing consolidation has allowed it to revert toward the mean. This could provide more room for further gains if Bitcoin manages to push higher.
Tariffs
This week’s Situation Report wouldn’t be complete without addressing the impact of the newly imposed tariffs on imports from Canada, Mexico, and China. For two consecutive weekends, market-moving news has emerged, sending prices lower. First, it was the DeepSeek AI news, and this weekend, the tariffs.
While President Trump had previously announced his intent to impose tariffs, the market was uncertain about the specifics. Would they be implemented gradually, with an effective date further in the future, or would high tariffs be imposed abruptly? It turned out to be the latter. This raised another question: was this a bargaining strategy or a long-term policy shift? On camera, Donald J. Trump stated that Canada and Mexico could do nothing to prevent the tariffs from taking effect.
With a strengthening dollar and growing market uncertainty, many risk assets sold off, including Bitcoin— which is the most liquid asset, tradable 24/7. However, after calls with Mexican and Canadian leaders on monday, during which they pledged to reinforce border security, Trump delayed the tariff’s effective date by 30 days, leading to a market rebound.
DXY
Let’s take a look at how the DXY has been behaving lately. Since early October 2024, the DXY has risen from 100 to 110, a level it reached in early January. However, after Trump took office, the DXY began to decline, ultimately leading to a breakdown of the uptrend.
https://blossom.primal.net/0792ea022d78637290860b2f59e0bd95567a55ceb4f93a493df878e5db782b1e.png
A stronger dollar generally signals contracting global liquidity. Since a significant portion of global debt is denominated in dollars, a stronger dollar (relative to other fiat currencies) makes it harder for corporations earning revenue in other fiat currencies to service their debt. This, in turn, slows down—or even reverses—their ability to invest.
Take note of the sharp spike at the beginning of this week, which briefly pushed the DXY back to nearly 110. This move followed the tariff news but was fully retraced after the announcement that tariffs would be delayed by 30 days.
US10Y
This brings us to another highly impactful factor in financial markets: the yield on the 10-Year Treasury Note. There has been extensive discussion about this yield, with crypto OG Arthur Hayes predicting in his blog that it would rise due to a confrontation between the Trump administration and Federal Reserve Chairman Jerome Powell. He argued that this temporary spike in bond yields could trigger a mini-financial crisis, sending all markets lower and pushing Bitcoin back to the $70,000 mark.
https://blossom.primal.net/e3b3c4247d876f986464f033c11c87f29f1b393504c7bd8076bab93892d996b3.png
President Trump has long been vocal about his demand for lower interest rates. To achieve this, he needs the Federal Reserve to ease policy and bring rates down. However, the Fed operates under a dual mandate: maintaining a healthy labor market while keeping inflation under control. If the Fed lowers the central bank funds rate too aggressively, bond vigilantes may step in and demand higher yields to compensate for rising inflation expectations. This would backfire on Trump’s demands and put the Fed in a difficult position, as it would no longer be acting in the best interest of the American people in terms of inflation control.
On the other hand, @nostr:npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83a wrote a piece on Fiscal Dominance, explaining that when government debt levels become too high, the Federal Reserve’s traditional tools lose their effectiveness. A rise in interest rates would only inject more cash into the system, as higher interest costs flow to bondholders, potentially exacerbating inflationary pressures rather than containing them.
That being said, for now, rates are coming down. Recently, the newly appointed Crypto Czar addressed the media, discussing plans to regulate stablecoins to reinforce U.S. dollar dominance in the global economy. This move could increase demand for U.S. Treasuries, potentially leading to lower rates due to a higher bid for these assets.
To monitor whether the trend is truly reversing, I use an inverse 180-day exponential Hull moving average. While I wouldn’t say you can apply traditional technical analysis to yields, this approach could help identify when rates are rolling over.
Economic data
This week, some important economic data was released. Inflation in the EU came in 0.1% higher than expected. Meanwhile, ISM Manufacturing in the U.S. exceeded expectations with a reading of 50.9—anything above 50 indicates expansion.
https://blossom.primal.net/3fe144e2921ca919e4c7428fbfbcbf2ab0aaaf8d61ee85dba87ec5fc1af24128.png
JOLTs data came in slightly lower than expected. While this might seem like negative news, stocks rallied slightly in response. The reason? A weaker labor market could encourage the Federal Reserve to ease policy, aligning with its mandate.
ISM Services also came in slightly below expectations, which has a dual impact. On one hand, it helps prevent inflation from overheating. On the other, it signals slightly lower revenue for companies providing these services.
On Friday, the Non-Farm Payrolls report and Unemployment Rate will provide further insights into the state of the labor market.
Short Term Holder Behaviour
To start, I want to give a shoutout to Kibo Money @nostr:npub1jagmm3x39lmwfnrtvxcs9ac7g300y3dusv9lgzhk2e4x5frpxlrqa73v44
I use some of the on-chain data provided by Kibo Money, who is developing an open-source on-chain analysis software that you can run on your own server. Check it out and send him some sats!
There’s a lot of alpha to be gained from analyzing the behavior of Short-Term Holders (STHs)—those holding coins that have moved recently (within the last 155 days). A study by Glassnode found that after 155 days, holders are more likely to keep their Bitcoin for the long term, making them less likely to sell.
https://blossom.primal.net/bdc6dd57317079c5cc1b05c04ed610a5765e9002f81471648863109f3286bc32.png
The Cost Basis (CB) for Short-Term Holders is currently around $92,000. When STHs have significant unrealized gains, they tend to sell for profit, adding selling pressure to the market. However, they also tend to sell at a loss, lacking the conviction of seasoned hodlers. While these are assumptions, the data shows a correlation, leading me to infer causation. It’s also possible that some of these coins belong to high-conviction Bitcoiners who are simply swing trading a portion of their holdings—taking profits when the price surges or cutting losses when the price drops. Either way, recently moved Bitcoin tends to move again in the near future.
https://blossom.primal.net/d762b5629858c21a45e23a35f2d1d4a806699466bab2d2449172e3dee82f1c32.png
The Short-Term Holder Spent Output Profit Ratio (STH SOPR) chart provides insight into when profit-taking occurs, as well as when investors capitulate and sell at a loss. It may seem straightforward, but when there’s a significant amount of unrealized profit—meaning the market price is well above the cost basis—one could take some chips off the table. Conversely, if one believes the long-term uptrend is still intact, while Short-Term Holders are panic-selling at a loss, it may be an opportunity to be greedy when others are fearful.
In a bull market, the Short-Term Holder Cost Basis (STH-CB) often acts as support during pullbacks. This makes sense because as portfolios grow, investors feel confident buying more on dips in anticipation of the next leg up. The reverse is also true in a bear market—the STH-CB acts as resistance. When the price crashes and later recovers near their cost basis, many traders view it as a “Get Out of Jail Free” moment and sell at breakeven.
One could use the STH-CB as a risk-on/risk-off indicator, but it isn’t foolproof. For example, during the consolidation period in the summer of ’24, the price dipped below the STH-CB, yet the broader uptrend remained intact. This highlights the importance of understanding where we are in the larger market cycle—which brings us to the next topic.
Golden skies
I like gold. Here at The First Bastion, it’s all about sound money, and gold has always been the ultimate embodiment of it. Due to its unique properties, gold is the best proxy for money that we have. However, it isn’t perfect and comes with its disadvantages—its weight makes it difficult to transport, and it cannot be used for instant settlement. Despite these limitations, gold remains one of the most important assets in today’s financial system, serving as a neutral store of value and an insurance policy against defaults. Gold recently hit new all-time highs amid growing uncertainty surrounding tariffs, wars, policy shifts, and escalating trade tensions.
Many investors see two possible outcomes:
-
The structural issues at hand cannot be resolved, leading to defaults by corporations and nation-states—prompting investors to buy gold as insurance against these defaults.
-
Policymakers will intervene with short-term fixes, likely in the form of quantitative easing. While this may temporarily stabilize the system, it will also erode purchasing power, making gold a hedge against monetary inflation.
So gold is ripping once again, and at this pace, it looks poised to reach $3,000 per ounce in the near future.
https://blossom.primal.net/74d6b51658d24c80e6ed9d25483921bfacf4ce8080d8ccc5534541bd1db40a19.png
BTC / GOLD
I love Bitcoin. It has the potential to become an even better proxy for money than gold. While gold is not easily verifiable—a key reason why it is inferior to Bitcoin as a form of money—it still has a market cap that is ten times larger than Bitcoin’s. Since gold cannot be easily manipulated (aside from physically mining it), its inflation rate remains around 2% per year. This makes it a solid benchmark for comparing Bitcoin’s real value growth, rather than just its dollar-denominated appreciation.
https://blossom.primal.net/5628178a098df954f59b6415b61c3cb810ad89a3f410b26be9267849334a8063.png
Behold the BTC/GOLD Power Trend. This power trend is based on calculations by Stephen Perrenod. The BTC/GOLD price follows a statistically significant power trend, which, according to historical data, currently sits at approximately 49.21 ounces of gold per Bitcoin. At today’s gold price, this translates to a staggering $140,000 per Bitcoin.
To be clear, this doesn’t provide certainty. All models are wrong, but some are useful. Many factors could shift this trend, and it will only hold if Bitcoin’s adoption rate continues at the same pace as in previous years. That said, it can serve as a valuable directional compass.
Remember when I mentioned the Short-Term Holder Cost Basis (STH-CB) as a risk-on/risk-off indicator? You could refine that approach by only applying it when Bitcoin’s price is above the BTC/GOLD power trend as a potential topping signal—or below it as a bottoming signal.
As of today, Bitcoin is valued at 34 ounces of gold per BTC—which is below the first cycle top of 2021 ($63,000) and near the March ‘24 local top ($73,000). The BTC/USD price currently sits around $98,500.
You see where I’m going with this, right?
Expected Outcome
I approach the market with probabilities. I try to imagine what is possible and then assess what is probable. Moving forward, I’ll include my probability-based assessments in every SitRep. The goal isn’t to convince you of my opinion (on the contrary—remember my disclaimer), but rather to practice forming an informed perspective so that you can position yourself in alignment with your own assessment.
Arthur Hayes recently estimated a 30% Bitcoin drawdown to be 60% likely. However, he made that assessment a few weeks ago, so his view may have evolved. After Monday’s events, I think it’s clear that Bitcoin is significantly impacted by policy changes—so one should prepare for volatility. But at the same time, Bitcoin’s rapid recovery, driven by strong buying pressure from Coinbase users, was almost unmatched by any other asset. Bitcoin is playing in the Champions League now, which means even greater correlation with macroeconomic factors.
A breakdown toward $70,000 is possible, but not probable. That would be a minus-one-sigma move on the BTC/GOLD Power Trend—a level previously seen during the COVID crash and the Terra Luna collapse. The recent grey swan events, like the DeepSeek AI news and tariffs announcement, only pushed Bitcoin down to $92,000. Based on this, it seems like it would take a mini-financial crisis—along with the US 10-Year Treasury Yield (US10Y) hitting 6%, as Hayes suggested—to drive Bitcoin significantly lower.
Meanwhile, gold is surging into price discovery with no signs of slowing down. Bitcoin has followed gold’s trajectory—just with a slight delay.
Bullish Catalysts for Bitcoin I didn’t cover them in this SitRep, but there are several bullish developments for Bitcoin, including:
- The creation of an American Sovereign Wealth Fund
- New and favorable SEC guidelines on crypto in the making
- A possible Bitcoin Strategic Reserve
- An increasing number of corporations adding Bitcoin to their balance sheets as a Treasury asset
- Potential favorable policy on stablecoins, strengthening the digital asset environment
- A push for lower US10Y yields, as discussed by Jeff Park
The market is likely to remain messy, with ongoing discussions about tariffs and policy changes.
But there’s one thing that keeps me thinking. Despite a bullish outlook, the price isn’t moving higher on good news—a signal that shouldn’t be ignored. It suggests that investors who want exposure to Bitcoin already have their positions. In other words, there’s a lack of new money flowing in. Without fresh demand, any negative news could tip the scales toward selling, exacerbated by momentum traders and liquidations.
Demand for neutral, scarce, and highly desirable assets—like gold—is clearly increasing. Bitcoin needs to capture some of that demand, too. That’s why I’m watching the DXY, US10Y, and GOLD like a hawk.
Stay sound,
J.M. Bergman
-
-
 @ 5d4b6c8d:8a1c1ee3
2025-02-07 14:02:05
@ 5d4b6c8d:8a1c1ee3
2025-02-07 14:02:05Apparently, there's still another NFL game and, I suppose, we have to discuss it.
I'm much more excited to get into all the NBA trades that happened. Who got better? Who got worse? Who did something really weird?
Of course, we'll talk about the contests going on in the territory.
MLB's ramping up. Can anyone challenge the Dodgers?
Ovi is trying to get back on pace to break NHL's career scoring record.
Any bets we're excited about
Plus, whatever the stackers want us to cover (time and memory permitting)
originally posted at https://stacker.news/items/878674
-
 @ e7bc35f8:3ed2a7cf
2025-02-07 14:29:10
@ e7bc35f8:3ed2a7cf
2025-02-07 14:29:10The strategic importance of Syria in shaping the balance of power in the Middle East is undeniable. Positioned at the crossroads of key regional players, Syria has long been a battleground for competing interests. From its alliances with Russia and Iran to its role in energy politics, the country has been targeted by external forces seeking to reshape the region to their advantage.
Syria has historically been an essential ally of Russia, providing the Russian navy access to the Mediterranean through the port of Latakia. At the same time, Iran has viewed Syria as a critical component of the so-called "Shiite Crescent," which provides Tehran with a vital connection to Hezbollah in Lebanon. Any disruption in Syria would have significant consequences for both Russian and Iranian strategic interests.
On August 31, 2011, Amnesty International released a report accusing the Syrian government of being responsible for the deaths of 88 detainees from recent protests. However, like most media narratives surrounding the conflict, the allegations were based entirely on second-hand accounts and contextless video snippets provided by opposition forces actively attempting to overthrow the Assad government.
Despite the lack of concrete evidence, the establishment media eagerly propagated the story, fueling calls for "humanitarian intervention." This followed a familiar pattern: the invocation of the so-called "Responsibility to Protect" doctrine, a pretext used by global powers to justify military invasions and devastating bombing campaigns under the guise of protecting civilians.
As seen with Libya, Western leaders—including Obama, Sarkozy, Cameron, and Harper—called for Assad's removal, paving the way for potential NATO military intervention.
Long before the Arab Spring, Western governments had been laying the groundwork for regime change in Syria. In April 2011, a U.S. State Department official admitted to running a two-year, $50 million program aimed at equipping protesters with new technologies to evade government detection. The same official revealed that activists from Syria and other Arab Spring countries had received training just before the uprisings began.
Earlier that year, The Washington Post published leaked U.S. diplomatic cables proving that Washington had been secretly funding Syrian opposition groups since at least 2005—well before the so-called "spontaneous" protests erupted.
This raises a critical question: why would an isolated government facing the threat of NATO intervention deliberately provoke the West by ordering snipers to fire on unarmed protesters at funerals? The mainstream media never questioned these dubious claims, which were sourced from anonymous, second-hand, and unverified reports.
n 2010, a group called Gen Next (renamed now as Alder) which has been involved with Alliance of Youth Movements in organizing youth-led destabilization campaigns in countries that are not friendly to American and Israeli interests had delivered a training program in which participants were taught how to handle high-powered sniper rifles and shoulder-mounted grenade launchers. Predictably, these reports were ignored in the West.
In August 2011, Israeli intelligence-linked outlet DEBKAfile reported that NATO and the Turkish military were drafting plans for a military campaign in Syria, which included arming opposition fighters with anti-tank and anti-air rockets, mortars, and heavy machine guns.
As the situation escalated, the establishment media once again cheered on war, pushing for intervention under the guise of protecting Syrian civilians. The cycle repeated itself in 2013, when Western governments accused Assad of using chemical weapons, conveniently ignoring the overwhelming opposition to another military adventure.
By 2013, the American public had grown weary of endless wars. Despite relentless efforts by the White House to manufacture consent for a unilateral strike on Syria, there was widespread opposition—not just in the U.S., but globally.
John Kerry and Barack Obama falsely claimed that Assad was responsible for a chemical weapons attack, using this as a pretext for military intervention. However, independent analysts and insiders exposed this as a false flag operation. Even in the UK, the propaganda push faltered when British Prime Minister David Cameron lost a crucial parliamentary vote on military action in Syria.
As more evidence surfaced, it became clear that the attack had been perpetrated by U.S.-backed terrorist groups—and that the U.S. government knew about it in advance. When even members of the British Parliament called out the deception, the war narrative collapsed, exposing the extent of the manufactured crisis.
The events in Syria were not isolated. Retired U.S. General Wesley Clark famously revealed that he had overheard a conversation at the Pentagon about a plan to invade seven countries—including Iraq, Libya, and Syria—long before the Arab Spring. While Clark’s timeline was not entirely accurate, the overarching strategy of destabilization was clear.
Key figures in the U.S. defense establishment at the time—including Paul Wolfowitz, Douglas Feith, and Richard Perle—had extensive ties to Israel, raising the question of whether a broader Zionist agenda was at play. Documents such as the infamous "Oded Yinon Plan" (Greater Israel) outlined strategies for the dissolution of Syria and Iraq into ethnically and religiously divided territories, weakening any potential opposition to Israeli expansion.
The plan explicitly called for breaking Syria apart into sectarian statelets, mirroring the strategy used to divide Lebanon. The long-term goal was clear: to ensure that Israel’s adversaries remained fragmented and powerless.

"Divide and conquer" is a strategy used for millennia. And this is what happens in Syria so many years as we were seeing the Sunni majority fighting the Alawite sect in Power under Assad and his father for decades. And it's interesting to see not only the native inhabitants Sunni of Syria but of course the foreign funded jihadists who were being shipped into the country and fueling all that conflict.
Part of what this was about, it's the destabilization of the Shia land bridge that connects Iran all the way to its Hezbollah forces in Lebanon, which runs through Syria. But if that can be destabilized and the Shia Alawite sect minority that rules Syria can be replaced with a Sunni majority ruling over the country then that would break up that link between Iran and Lebanon and further destabilize and isolate Iran.

And this is something that can be seen in policy planning documents of various think tanks, as in the infamous "Which path to Persia?" document from Brookings Institution.
As we start to expand the scope of this, then of course the thing that always in these Middle East conflicts comes into play is the natural resources. Let's remember the prospect of the Iraq, Iran, Syria pipeline. Iran, Iraq, and Syria had signed a deal for the construction of the Middle East’s largest gas pipeline, which would transit Iranian gas from Iran’s South Pars gas field to Europe via Lebanon and the Mediterranean Sea.
What we were talking about back then was a pipeline providing traveling from Iran to Europe, through the Mediterranean. That move was about to change the power balance of the region. Such a project had the potential to shift the regional power balance dramatically. The mere prospect of it was enough to anger multiple stakeholders, from the U.S. and Israel to Turkey and the Gulf monarchies, all of whom had vested interests in preventing Syria from becoming an energy corridor.
The war in Syria was never about democracy, humanitarian concerns, or chemical weapons. It was about power, control, and the relentless pursuit of strategic dominance by Western and regional actors. The destabilization of Syria served multiple agendas—weakening Iran, severing Russia’s influence, ensuring Israel’s security, and controlling energy routes.
What we have witnessed over the past decade is not a civil war, but a foreign-orchestrated campaign to dismantle yet another independent state in the Middle East. Understanding these dynamics is essential in recognizing how mainstream narratives are crafted to justify war while hiding the real motivations behind the chaos.

-
 @ 044da344:073a8a0e
2025-02-07 14:06:14
@ 044da344:073a8a0e
2025-02-07 14:06:14Knapp ein Jahr hat es gedauert nach meinen letzten Gesprächen im Apolut-Studio, seinerzeit mit Robert Cibis und Yann Song King und am Rande von Berlin schon längst nicht mehr so komfortabel wie einst an der bayerisch-österreichischen Grenze oder dann im Süden Schwedens, wo eine komplette Mannschaft für perfekte Qualität gesorgt hat. Kamera, Ton, Regie, Maske und sogar eine Gästebetreuung. Lauter Profis, aber irgendwann offenbar nicht mehr zu bezahlen aus Spenden und wahrscheinlich auch überholt von der Konkurrenz im Internet, die mit einfachen Mitteln zwar weit unterhalb aller TV-Standards bleibt, aber aktuell ist, viel, viel günstiger und inhaltlich trotzdem sehr oft sehr spannend.
Egal. Auf Onlineinterviews hatte und habe ich keine Lust. Ich möchte den Menschen spüren, um den es geht. Vorher mit ihm reden und hinterher hoffentlich auch noch. Ich telefoniere nur im Notfall, weil dort vieles von dem verlorengeht, was den Austausch ausmacht. Zoom und Co. liefern zwar ein Bild, sind aber ansonsten nicht viel besser. Um das nur mit einer Zahl zu illustrieren: Bei einem Bildschirmgespräch dauert es zweieinhalb Sekunden, bis mein Gegenüber registriert, dass ich etwas sagen will. Live und in Farbe liegt die Reaktionszeit bei knapp der Hälfte.
Also habe ich aus der Not eine Tugend gemacht und bin selbst zum Produzenten geworden. Nicht ganz allein natürlich. Es gab Tipps von Dirk Wächter, der für viele der Bilder und Videos von Daniele Ganser steht und die Apolut-Gäste auf unnachahmliche Weise fotografiert hat, von Paul Brandenburg, der Technik borgte, und von Ingmar Beyer, den ich im großen Studio kennenlernen durfte und der nun auch bei meinen eigenen Versuchen dafür sorgt, dass der Ton stimmt. Vielen Dank dafür.

Ein Dank gilt auch Axel Klopprogge, den die Leser dieser Seite aus der Kolumne Oben & Unten kennen und der sich gewissermaßen als Versuchskaninchen zur Verfügung stellte. Der Anlass war denkbar günstig, als wir uns Ende Januar im Wohnzimmerstudio trafen: Gerade war seine Aufsatzsammlung „Links oder rechts oder was?“ erschienen – Stoff genug für 90 Minuten. Das Buch wird morgen in meiner Kolumne noch einmal gesondert gewürdigt.
Wer in unser Gespräch hineinschaut, wird schnell den Unterschied zu Apolut sehen: Es gibt Publikum. Gut zehn Menschen, die hoffentlich wiederkommen. Die nächsten Gäste: Michael Beleites, mit dem ich über den Darwinismus reden werde und über all das, was diese Ideologie aus uns gemacht hat, sowie Erich Hambach, der gerade auf den letzten Metern für sein Buch „Herren des Geldes“ ist.
-
 @ 54286b98:3debc100
2025-02-07 11:05:29
@ 54286b98:3debc100
2025-02-07 11:05:29Reality is clear when we stand in the light.\ Falsehood appears when we tilt ourselves just enough to distort what’s real.
Every object—tree, person, or building—casts a shadow.\ But only the object is real. The shadow is an effect, not the truth.
Light reveals what’s true. Darkness hides it, warping our perspective.\ Our angle to the light source changes everything.
Christ is that source of light. He shines on everyone—no matter who we are.\ He doesn’t shift. Truth doesn’t shift.
But we do. Our minds waver like waves in the ocean, creating ever-changing shadows.\ Those shifting shadows can fool us.
Today, let’s choose to stand in his perfect light.\ Let’s notice where we need to grow and refuse to be deceived by distorted reflections.\ Let’s anchor ourselves to what’s real.
Until next time,\ J
Do not be deceived, my beloved brothers. Every good gift and every perfect gift is from above, coming down from the Father of lights, with whom there is no variation or shadow due to change. Of his own will he brought us forth by the word of truth, that we should be a kind of firstfruits of his creatures. James 1: 16-18
Original article published on: https://www.javierfeliu.com/blog/shifting-shadows/\ Photo by Yang Deng / Unsplash
-
 @ a367f9eb:0633efea
2025-02-07 10:39:28
@ a367f9eb:0633efea
2025-02-07 10:39:28Issued on January 23, 2025, Staff Accounting Bulletin 122 rescinds SAB 121, originally issued by Gensler in March 2022. The previous bulletin provided guidance for financial entities and custodians holding any “crypto-assets,” requiring them to account for all cryptocurrencies primarily as liabilities on their balance sheets, rather than assets.
The revoking of SAB 121 empowers entities to assess whether their crypto-assets are classified as liabilities only if they believe a loss is probable.
For bitcoin holders who hold their own keys and run their own node, this distinction and its subsequent repeal made little difference.
But for the budding world of Bitcoin banking and finance, as well as the booming industry of custodial wallets and brokerages, it’s a game changer.
Rather than having to match cryptocurrency deposits one-for-one with other liquid assets in the case of a contingency, the new accounting guidance frees up institutions to mark the true values of crypto-assets on their books.
Rather than having to buy up $1 million in treasuries or cash in order to hold $1 million in bitcoin or cover losses, firms will now be able to recognize that $1 million as a true asset.
It may not seem like a revolution, but it may be the beginning of our bull-inspired Bitcoin banking era.
After years of byzantine persecutions of cryptocurrency developers, entrepreneurs, and ever-increasing regulations on Bitcoin, this paradigm shift at the nation’s premier markets regulator means traditional finance can finally include bitcoin and its crypto-offspring in its suite of financial products – with some caveats.
Practically, this rather benign-sounding rule lowers the barrier of entry for entities that want to offer bitcoin services to their customers. Whether it’s a bank, an exchange, or a liquidity service provider custodying funds, there is now a more sustainable path for offering bitcoin alongside any other type of account.
While a general crypto market framework is still far from established in law, the current situation grants fairness between both fiat money and cryptocurrencies in the hands of entrepreneurs who want to custody funds for their clients.
Practically, however, what does this mean for the average bitcoiner?
What will my Bitcoin bank look like?
If we take a peek over at Europe, there are already FinTech firms and banking institutions that offer some level of bitcoin services.
Xapo Bank, a private bank headquartered in Gibraltar, offers each customer a traditional bank account and IBAN number alongside an instantaneous deposit and withdrawal address for Bitcoin and Bitcoin Lightning, Tether, and USDC.
Considering Xapo built the doomsday-proof custody vaults for bitcoin storage later bought by Coinbase in 2019, now the preferred institutional custodian for billions in assets, it’s easy to see why so many customers trust their custody.
And for those willing to make the tradeoff for custody of their funds, they do offer something attractive.
In a single account, a customer could deposit cash, exchange it to bitcoin, and withdraw to self-custody. They could also deposit bitcoin using Lightning, and then instantly convert that amount to send a traditional bank transfer to pay their rent or utility bills for those who don’t yet accept bitcoin.
Again, this may not be the solution for those who prefer self-custody, but it does offer an integrated fiat on and off ramp that others may find convenient.
Similarly, the UK-based FinTech firm Revolut offers its customers the ability to deposit and withdraw their bitcoin within the app, as well as exchange it for whichever fiat currency they wish. For those who currently hold bitcoin in an ETF or some other custodial product, a move to an app such as this may be even more attractive.
And we already know US companies are begging to expand their own services to their customers.
Companies such as Strike and Fold have already begun to increase their Bitcoin banking services for American customers, offering account and routing numbers for bill pay, as well as the ability to instantly swap between currencies if they wish.
Fold has the ambition to become one of the nation’s largest publicly-traded bitcoin financial services, looking to soon add mortgage and lending offers, as well as insurance solutions.
These financial firms will offer bitcoin for purchase, lending, and exchange, but we can also assume their suite of products will become more diverse and attractive for a more diverse customer base.
What about sovereign money?
Educating Americans about the benefits of Bitcoin is an important task. So is improving our policy landscape so that all bitcoiners may flourish.
But if the Bitcoin network truly represents a revolutionary way to have and use neutral money, should we even consider Bitcoin banks something we want? How can peer-to-peer money integrate with the centralized custodial banking system so many of us are trying to escape?
Even the most primitive advantages of Bitcoin are built on its ability to be owned in a sovereign way, at the total exclusion of everyone who doesn’t have the private key. For many of us, this is all we desire and want. And for the rights to hold and use Bitcoin how we wish to be universally recognized.
However, we cannot dictate how the rest of our Bitcoin peers will engage with the network, nor what they inscribe into blocks if they have the computing power to mine them. If Bitcoin entrepreneurs freely compete to offer unique products and services to custody, trade, or lend bitcoin, the rules should make that easier and more possible.
For those who will still need to interact with the fiat world, they should be able to benefit from Bitcoin-first products and services designed with them in mind. And regulations should empower them rather than restrict what they can do.
Not every Bitcoin banking product will be attractive to every bitcoiner and that’s okay. But the positive evolution of e-cash, custodial services, lending, and insurance is something that will help leverage the power of Bitcoin. And that should be championed.
Yaël Ossowski is a fellow at the Bitcoin Policy Institute.
This article was originally published at the Bitcoin Policy Institute.
-
 @ d360efec:14907b5f
2025-02-07 09:42:54
@ d360efec:14907b5f
2025-02-07 09:42:54ณ ดินแดนอันไกลโพ้น ปรากฏดันเจี้ยนลึกลับไร้ก้นบึ้ง นามว่า "ตลาดการเก็งกำไร" ประตูทางเข้าเปล่งประกายล่อตาล่อใจ แต่มักถูกปกคลุมด้วยหมอกแห่งความไม่แน่นอน
คำจารึกโบราณ แกะสลักเหนือประตูทางเข้า เตือนสติผู้มาเยือน: "ผู้ใดเข้าล้วนมิอาจหวนคืน..." เฉกเช่นสำนวนโบราณที่กล่าวขาน "คนในมิอาจออก คนนอกมิต้องการย่างกราย"
ภาพที่ปรากฎตรงหน้า คือชายหนุ่มผู้หาญกล้า กำลังจะก้าวเข้าสู่ประตูดันเจี้ยน เหนือประตูมีป้ายขนาดมหึมาสลักคำว่า "Trading" สัญลักษณ์แห่งโลกการลงทุน การเก็งกำไร ไม่ว่าจะเป็น หุ้น, ฟอเร็กซ์, คริปโต ล้วนเป็นมอนสเตอร์ที่สถิตอยู่ในนี้
การจะพิชิตดันเจี้ยนนี้ได้นั้น หาใช่เรื่องง่าย ภารกิจแรกคือการกำจัดปีศาจ"นักพนัน" ที่สิงอยู่ในจิตใจของผู้กล้าทุกคน ปีศาจตนนี้ร้ายกาจยิ่งนัก แต่มิใช่ว่าไร้ทางปราบ หากท่านผู้กล้าปรารถนาจะหลุดพ้นจากวงจรอุบาทว์นี้ จงใช้วิธีเหล่านี้เถิด
- เข้าใจว่าการพนันคือกับดัก
ปีศาจพนันมักล่อลวงด้วยภาพลวงตาแห่งชัยชนะเพียงชั่วครู่ แต่แท้จริงแล้ว มันถูกออกแบบมาเพื่อสูบเลือดสูบเนื้อจากเหล่าผู้กล้าในระยะยาว จงจำไว้ว่าการพนันมิใช่หนทางสู่ความร่ำรวย แต่เป็นเส้นทางสู่หุบเหวแห่งความสิ้นเนื้อประดาตัว
- เปลี่ยนมุมมองเกี่ยวกับเหรียญทอง
จงมองเหรียญทองที่ท่านมีมิใช่แค่ตัวเลข แต่เป็น “เวลาและหยาดเหงื่อ” ที่ท่านได้แลกมา หากท่านสูญเสียมันไปเพราะการพนัน มันคือเวลาชีวิตที่หายไปตลอดกาล
- ตัดขาดสิ่งเร้าที่กระตุ้นให้เล่น
• ลบแอปพนัน / ปิดกั้นเว็บไซต์มืด • เลิกติดตามเพจหรือกลุ่มที่เกี่ยวข้อง • เปลี่ยนสหายร่วมทางที่ชักชวนไปสู่ทางเสื่อม
- ใช้กฎ 5 นาที
เมื่อใดที่ความกระหายอยากเล่นครอบงำ จงหยุดยั้งตัวเองไว้ 5 นาที แล้วตรองดูว่า • คราก่อนท่านสูญเสียไปเท่าใด? • หากเล่นแล้วเสียอีก จะรู้สึกเช่นไร? • มีสิ่งใดที่ควรทำมากกว่านี้หรือไม่?
- แสวงหาเส้นทางแห่งการลงทุนที่แท้จริง
แทนที่จะใช้เหรียญทองไปกับการพนัน จงเปลี่ยนเป็นการลงทุนที่มีโอกาสเติบโต เช่น เป็นนักรบแห่งคุณค่า (VI) , เข้าซื้อหุ้นแล้วเก็บมันไว้ในหีบสมบัติ 1 ปี , DCA BTC ดั่งสะสมขุมทรัพย์ทีละน้อย
-
ถามตัวเองว่า “อยากเป็นผู้ชนะ หรือเป็นเหยื่อ?” ผู้ที่ร่ำรวยจากการพนันคือนักลงทุนผู้เปิดบ่อน มิใช่ผู้เล่น หากท่านปรารถนาจะเป็นผู้ชนะ จงเลือกเส้นทางที่ชาญฉลาดกว่า
-
ตั้งเป้าหมายที่ยิ่งใหญ่กว่า
จงตั้งเป้าหมายที่ชัดเจน เช่น สะสมเหรียญทองเพื่อซื้อปราสาท 5 ล้าน หรือหาเงิน 100 ล้าน แล้วจงมุ่งมั่นไปที่มัน การพนันจะทำให้เป้าหมายของท่านล่าช้าลง
📉 เหตุใดดันเจี้ยนแห่งการเทรดจึงเปรียบเสมือนเขาวงกต?
1️⃣ ก้าวเข้ามาง่าย ออกไปยาก
• การเข้าสู่ตลาดการเงินเป็นเรื่องง่ายดาย ใช้เพียงบัญชีเทรดและเงินทุนเพียงเล็กน้อย แต่เมื่อเข้ามาแล้ว จิตวิทยาแห่งการลงทุน และ ความผันผวนของตลาด จะทำให้ยากที่จะออกไป
2️⃣ เส้นทางที่ซับซ้อน
• นักรบมือใหม่มักคิดว่าการทำกำไรเป็นเรื่องง่าย แต่เมื่อเริ่มต้นจริงจะพบว่ามีปัจจัยมากมายที่ต้องเรียนรู้ ทั้งเทคนิค เวทมนตร์พื้นฐาน อารมณ์ตลาด และจิตวิทยาของตน
3️⃣ ความโลภและความหวังทำให้ติดอยู่ในตลาด
• หลายคนเริ่มต้นเทรดด้วยเป้าหมายหาเหรียญทอง แต่เมื่อขาดทุน กลับพยายามเอาคืน • เมื่อกำไร ก็อยากได้มากขึ้น จนบางครั้งไม่รู้จักพอ
4️⃣ ไม่มีเส้นทางที่แน่นอน
• ในเขาวงกตนี้ ไม่มีทางเดินตรงไปสู่ความสำเร็จ ต้องลองผิดลองถูกหลายครา • บางคนหลงทาง บางคนเจอทางตัน บางคนออกจากตลาดไปก่อนจะถึงทางออกที่แท้จริง
🎯 แล้วจะเอาตัวรอดจากวงกตนี้ได้อย่างไร?
✅ เข้าใจว่าเทรดไม่ใช่การพนัน • การเทรดที่ดีต้องมีระบบ ไม่ใช่แค่เสี่ยงดวง ✅ ฝึกวินัยและจัดการอารมณ์ • สิ่งที่สังหารนักรบมิใช่ปีศาจในตลาด แต่เป็น “อารมณ์ของตนเอง” ✅ วางแผนก่อนเข้าเทรด และมีจุดตัดขาดทุนเสมอ • อย่าเข้าเทรดโดยไร้แผน เพราะจะทำให้ท่านติดอยู่ในเขาวงกตตลอดกาล ✅ รู้ว่าเมื่อไหร่ควรหยุด • บางครั้ง “การไม่เทรด” คือการตัดสินใจที่ดีที่สุด
🔮 บทสรุป
ดันเจี้ยนแห่งการเทรดเปรียบเสมือนสถานที่ลี้ลับที่ยังไม่มีผู้ใดสำรวจมาก่อน ผู้ใดที่ย่างกรายเข้ามาล้วนออกไปยาก เพราะมันเต็มไปด้วยความท้าทาย อารมณ์ และความโลภ แต่หากท่านเข้าใจเกมนี้ดีพอ ท่านจะสามารถหาทางออก และเปลี่ยนมันให้เป็นโอกาสแห่งความมั่งคั่งได้ จงจำไว้ว่า การจะออกจากดันเจี้ยนนี้ได้ ท่านต้องพิชิตบอสใหญ่ "การรู้เท่าทันอารมณ์ และมายเซ็ทที่เหมาะสมกับเทรนด์เดอร์" ให้จงได้!
หวังว่าพวกท่านจะไม่หลายเป็นซากศพเน่าๆ ในดันเจี้ยนแห่งนี้
ของให้โชคดีมีชัยในโลกเทรนด์เดอร์ YONOSUBA
-
 @ 16d11430:61640947
2025-02-07 09:37:24
@ 16d11430:61640947
2025-02-07 09:37:24Introduction: The Lost Art of Flourishing
Eudaimonia, the Greek concept of human flourishing, represents a state of deep fulfillment derived from purpose, mastery, and moral virtue. Aristotle described it as the highest human good, achieved not through transient pleasures but through living in accordance with reason and excellence.
Yet, in our modern fiat-driven world, eudaimonia has largely perished. Instead of striving for excellence, people are entrapped by systems of debt, artificial scarcity, and wage slavery, where fulfillment is secondary to survival. The incentives of fiat capitalism—endless growth, consumerism, and bureaucratic control—have eroded the conditions necessary for human flourishing.
The purpose of this article is to explore the death of eudaimonia under fiat rule, supported by critical evidence, and to examine whether it can be resurrected—perhaps through alternative systems like Bitcoin and decentralized technologies.
The Fiat Machine and the Death of Eudaimonia
- The Extraction of Meaning: Fiat as a Mechanism of Control
Fiat currency, backed by nothing but government decree, is a tool of centralized power. It is inflationary by design, ensuring that those who hold wealth in fiat lose purchasing power over time unless they participate in increasingly speculative financial schemes.
This constant need to hedge against inflation forces individuals into short-term thinking, undermining long-term endeavors that lead to mastery and fulfillment. Instead of creating art, philosophy, or science for its own sake, people are incentivized to chase money in the fastest, most extractive way possible.
Critical Evidence: Wages have stagnated relative to productivity since the abandonment of the gold standard in 1971, while financialization has exploded. According to the U.S. Bureau of Labor Statistics, median wages have barely kept up with inflation, whereas asset prices (stocks, real estate) have soared—favoring the wealthy who can invest while punishing wage earners.
- The Death of Virtue: How Fiat Incentivizes Corruption
Aristotle tied eudaimonia to virtue—justice, courage, temperance, and wisdom. But fiat economies erode virtue by rewarding manipulation over integrity. In a world where money is easily printed, those closest to its issuance—the state, banks, and corporate elites—reap the rewards while the average person suffers debasement.
Fiat allows for moral hazard: banks are bailed out after reckless speculation, politicians spend without accountability, and corporations use inflation to justify price hikes. This destroys trust, a fundamental component of any thriving society.
Critical Evidence: The Cantillon Effect demonstrates that newly printed money benefits those who receive it first (banks, hedge funds) at the expense of those who receive it last (workers, pensioners). The 2008 financial crisis and subsequent bailouts exemplify how fiat rewards risk-taking elites while punishing ordinary citizens.
- Bureaucratic Slavery: The War Against Self-Sufficiency
Fiat governance has transformed human beings from self-reliant individuals into bureaucratic dependents. Governments and corporations engineer complexity—compliance laws, credential requirements, and licensing systems—to keep individuals trapped in cycles of employment and taxation.
Eudaimonia thrives in societies where individuals have control over their work and creations, yet fiat systems strip away autonomy. Most people today work jobs they do not love, merely to service debts or meet rising costs.
Critical Evidence: A 2019 Gallup survey found that 85% of employees worldwide are disengaged from their jobs, meaning they find no real meaning in their work. Meanwhile, U.S. student loan debt has surpassed $1.7 trillion, forcing young people into decades of financial servitude before they can even attempt to pursue meaningful work.
Can Eudaimonia Be Resurrected?
- Bitcoin and the Return of Hard Money
If fiat is the poison, Bitcoin might be the antidote. Unlike fiat, Bitcoin is scarce, decentralized, and operates on proof-of-work, rewarding merit rather than proximity to power.
A Bitcoin-based economy restores long-term thinking by allowing individuals to store value in a deflationary asset rather than being forced into high-risk speculation. When people do not need to chase inflation, they can focus on work that is intrinsically fulfilling rather than merely profitable.
Critical Evidence: Countries like El Salvador have adopted Bitcoin as legal tender to escape the inflationary policies of central banks, while Bitcoin’s fixed supply of 21 million ensures its purchasing power cannot be arbitrarily diluted.
- Decentralized Systems and Self-Sovereignty
Beyond money, decentralization itself is a means of restoring eudaimonia. Peer-to-peer networks, open-source software, and blockchain verification (such as DamageBDD) enable individuals to engage in meaningful work without needing corporate or governmental permission.
Critical Evidence: The rise of remote work, creator economies, and DAOs (Decentralized Autonomous Organizations) shows that people can be productive outside traditional corporate structures when given the right tools.
- The Renaissance of Craftsmanship and Knowledge
A return to hard money and decentralized economies will likely trigger a renaissance of craftsmanship. When individuals no longer need to rush for short-term profits, they can master trades, sciences, and arts in ways that have not been possible since the fiat era began.
We are already seeing glimpses of this in the resurgence of interest in sovereign computing, homesteading, and open-source development—a direct rebellion against the fiat model of centralization and planned obsolescence.
Critical Evidence: The growth of FOSS (Free and Open Source Software) and Bitcoin development reflects a shift toward work driven by passion and principle rather than extractive financial incentives.
Conclusion: The Path Forward
Eudaimonia is not dead, but it has been suffocated under the weight of fiat. By restoring individual sovereignty—through sound money, decentralized verification, and self-sufficiency—we can resurrect the human spirit. The transition will not be easy; it will require a rejection of the comfort fiat provides in exchange for the struggle that meaningful existence demands.
Yet, for those who seek mastery, virtue, and true fulfillment, there is no other choice. The fiat era has stripped humanity of its highest potential. It is time to reclaim it.
-
 @ 6ad3e2a3:c90b7740
2025-02-07 08:17:18
@ 6ad3e2a3:c90b7740
2025-02-07 08:17:18When I used to work in fantasy sports, people would ask me questions about their teams, e.g., which players to start, who to drop. What they didn’t realize is I had seven of my own teams to worry about, was already living and dying with my own myriad choices, good and bad, I made every week. The last thing I needed was to make a decision for them, see it go bad and suffer more on their account.
I’d tell them, “You decide, I’ve got my own problems.”
. . .
I don’t know what I’m doing. Ideas which feel like insights come to me, I try to articulate them to my satisfaction and post them (with some editing help from Heather.) Often I feel like I should be producing more work — after all, I don’t have a job any more, I have plenty of time. Walking the dog, exercising, managing your finances, picking up the kid, putting food on the table (literally) is well and good, but fulfilling your duties is not enough. You need to stay in the game. What game is up to each person, but it should be a game you enjoy, one that draws on skills honed over decades by the accident of your particular interests.
. . .
Writing and ideas can’t be produced on demand. I mean they can — and I did it for 22 years on a particular topic — but I don’t mean that kind of writing. I don’t want a schedule. I don’t need more rules, more discipline, more “hacks.” Discipline is like the interest on a 30-year mortgage. Initially it’s most of the payment, but over time it cedes weight to understanding which is like the principal. Discipline without understanding is like an interest-only mortgage. You pay it every month and get nowhere.
Even when insights arrive they can’t always be articulated sufficiently and coherently. Many insights are of the one sentence variety — fine for a social media post, but you can’t send out an email newsletter 10 times per day with one sentence insights. It doesn’t work over that medium.
That’s a dilemma because posting on social media doesn’t feel like proper work. Yes, you’re reaching people, affecting the zeitgeist in whatever small way — but there’s something addictive and unsatisfying about it, like eating candy instead of food. Don’t get me wrong, I stand by my posts (consider them organic, artisanal candy) but shitposting and the immediate feedback received therefrom keeps you only on the periphery. I need to connect with something deeper.
. . .
I’ve spent a lot of time dissecting the various pathologies of the laptop class, of which I’m obviously a part as I literally type this in a coffee shop on my laptop! The need to believe they are empathic and good overwhelming any rational sense-making and basic morals. Men dominating women’s sports, child sex changes, forced injections, criminals running rampant, cities in decay, calls for censorship and funding for foreign wars. The authorities patted them on the back, their peers accepted them and their overlords promoted them so long as they hewed to the narrative.
The freakout we’re presently witnessing is not about the billions in taxpayer money no longer being sent for DEI training in some foreign country, i.e., money-laundering to favored interests and cronies. They’re not really upset FBI agents are being fired, secrets are being revealed, that we are finally making an effort to prevent fentanyl from flowing across the border and killing our fellow citizens. These are good things, and even if you don’t agree, none of it is grounds for the meltdowns I see every day on social media.
What’s really happening is people who were assured they were the “good”, the empathic, the compassionate ones, those who towed the line during covid, got their boosters, wore their masks, “social distanced,” put pronouns in their bios, are being confronted with a terrifying realization: the behaviors and beliefs, to which they so dutifully attached themselves, for which they publicly and stridently advocated, whether online or at Thanksgiving dinner, are no longer being rewarded. In fact, they are being openly ridiculed. Instead of the pat on the back, increasingly Team Good is facing mockery and outright scorn.
There will be no legal consequences. No one will be arrested or put in a camp, delusions of persecution notwithstanding. If you produce real value for a real employer, you are not at risk of being fired. If you insist on perpetuating your derangement on social media you will not be deplatformed or canceled (that only happens to people speaking the truths inconvenient to the powerful.)
No, the reality is in some ways far worse: your entire worldview, on which you staked your self-image, is being dismantled in real time. You are no longer “good,” it’s becoming obvious to most the policies for which you advocated were catastrophic, the politicians for whom you voted deeply cynical and corrupt. The gaping abyss within your being to which you attached this superstructure of self-affirmation is dissolving into thin air. You are not “superior” like you thought, you are just another person suffering and existing like everyone else. And your only choices are to face that daunting reality or cling to a dying and useless paradigm, the end game for which is only madness.
We all want to feel good about ourselves, and like an obese person drugging themselves with high-fructose corn syrup for years, you have gorged on the distorted approbation of a sick society that, unpleasantly for you, is starting to heal. Your first laps around the track, so to speak, are going to hurt a lot.
. . .
I probably went on too long about the laptop class freakout. I have a lot of resentment toward the way they behaved the last five years. But I started this essay with the idea that I have my own problems, and in the end, I am not much different from them.
I want to produce more work, and of higher quality, but to what end? To feel good about my contributions, to have a sense that I am “good.” Maybe it’s not “good” in the lame “I complied with authority, and everyone likes me” kind of way, but it arises from the same source. That source is the emptiness within, wherein we require accolades, dopamine, positive feedback as a kind of justification for our existence. “No, I am not squandering my time on earth, living a comfortable life, I am asking hard questions, connecting with people, sharing hard-won insights. I am useful! I am good! I got my sixth dopamine booster from writing yet another essay!”
. . .
There is an irony in writing this piece. I feel as I type the cathartic nature of expressing these feelings. I am doing something worthwhile, everything is flowing out of me, the minutes are sailing by. I am identifying and solving this thorny problem simultaneously, engaging with the emptiness and dissatisfaction. The solution isn’t in the output, whatever one might think of it, it’s in giving attention to the feelings I’ve squandered too much time avoiding. I feel unworthy not because I do not produce enough work, it turns out, but because I am unwilling to connect with my deepest nature.
. . .
No matter how uneasy you feel, no matter how much fundamental doubt you have about your value as a human being, you can always start where you are. The feeling of unworthiness, the need for an escape, the craving for some kind of reward from your peers or the authorities or whatever easily-consumed carbohydrates you have in the kitchen is simply the present state in which you find yourself. It is not wrong or bad, it just is. And what is can always be examined, observed, given attention. Attending to that discomfort is always within reach.
. . .
The last thing I want to do is write an essay, face a purgatory of sitting down and consciously putting my feelings into words. It’s so much easier to distract oneself with all the news about the world, check 100 times a day the price of bitcoin and my other investments. But purgatory is the only way out of hell. The hell of wanting to succeed, of wanting to become “good.”
For some, that astroturfed worldview they so painstaking affixed to their empty souls is dissolving toward a revelation of the emptiness beneath. And unsurprisingly they are freaking out. But I’ve wasted too much time arguing with them, pointing out the ways in which they’re misinformed, driven by fear and derelict in their basic epistemic responsibilities. If you want to hold onto the lies you were told, knock yourself out. I’ve got my own problems.
-
 @ da0b9bc3:4e30a4a9
2025-02-07 07:26:07
@ da0b9bc3:4e30a4a9
2025-02-07 07:26:07Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/878449
-
 @ e3ba5e1a:5e433365
2025-02-07 05:25:58
@ e3ba5e1a:5e433365
2025-02-07 05:25:58How much does the government cost? Focusing just on the US, we could talk in terms of US dollars spent on the budget each year. But those numbers are so large we can’t really conceptualize them. A more relatable way of talking about this is what percentage of your income goes to the government. Or, even better, what percentage of your productive output is funneled to the government?
A first pass answer would be to look at income tax. If income tax is 30%, you work 30% of the year for the government and 70% for yourself. The problem is that income tax isn’t the only tax. There’s property tax, sales tax, payroll tax (i.e. another income tax), and who knows how many others. In other words, income tax only covers one (large) portion of our taxed income.
But it doesn’t stop there. We can’t forget inflation, the hidden, silent tax that not only erodes your earnings, but destroys your savings. It pulls off the amazing feat of not only taxing you today, but historically taxing you. It punishes you for being a prudent person and saving your money. (Which, side note, is why we love saving in Bitcoin.)
You might think we’re done. We’ve covered all the ways the government funds itself: direct taxation and inflation (via money printing). And that part is true. But we haven’t finished looking at the cost. You see, economically speaking, every time you put a tax into a system, you create inefficiencies. The market can no longer perform as well as it did previously. So we have yet another hidden cost: all productive capability in the economy gets worse, because the government needs to push its way in. An easy way to see this is all the tax games companies play to fall into different deductions and exemptions.
It doesn’t stop there either. Now that we’re talking about government-caused inefficiency, we can of course get to regulation. Regulation directly makes things more expensive (by forcing companies to spend time on compliance). It also indirectly makes things more expensive by presenting a barrier to entry for new providers, reducing competition and further hurting consumers.
Surely that’s the end, right? Nope. The government is sucking capital out of the private sector to put into public sector projects. That means the private sector has less capital for investment. People are incentivized not to save due to inflation, which encourages high-time-preference consumerism. This means we get less investment by companies for the future, which defeats the natural tendency of industry to become more efficient over time and pass on the savings to the consumer (via technology-driven deflation, for instance).
I knew all of that two weeks ago, and it hasn’t changed.
There’s one final piece to this puzzle. Many of us suspected it. With the news coming out about USAID and the programs it laundered money to, we’re starting to get even more concrete proof. The government steals our money, inflates it, takes all of that productive capacity we sweated and toiled for… and gives it to people who are actively trying to hurt us, yet again furthering the cost of government.
The cost of government isn’t one number. It’s not quantifiable. The cost of government is losing out on the world where everything becomes better, safer, cheaper, faster, healthier, and more enjoyable, and replacing it with a decaying, eroding society, where the most morally bankrupt people can fleece the rest of us for their livelihoods.
I’m praying that the exposure and toppling of USAID is a major accomplishment, but just one of many more to come. To quote The Two Towers, I hope it “will be like the falling of small stones that starts an avalanche.”
-
 @ 000002de:c05780a7
2025-02-07 03:54:22
@ 000002de:c05780a7
2025-02-07 03:54:22I've long been a fan of Liberty Maniacs, the site that makes funny political shirts for rebels & liberty lovers but their email today hit me as extra funny.
Here's what they shared.
To say the last two weeks have been wild would be the understatement of the century.
🔥 DOGE is taking over the Treasury
🔥 USAID got caught laundering money (again)—basically funding everything to the left of Jimmy Carter’s ghost.
🔥 The new AG wants to drop the Epstein list like it’s hot.
🔥 The CIA just casually admitted the government created COVID.
🔥 And oh yeah, the Gulf of Mexico? Not anymore. Welcome to the Gulf of America!
At this point, reality is outpacing satire. But don’t worry, we’re working harder than a WEF escort during Davos week to get these news cycles onto shirts before the next scandal drops.
Not sure if we’ll ever catch up, but damn it, we’re gonna try.
I mean, that's pretty good stuff. If you are a marketer or copywriter this is how you do it.
originally posted at https://stacker.news/items/878326
-
 @ 57d1a264:69f1fee1
2025-02-07 03:35:34
@ 57d1a264:69f1fee1
2025-02-07 03:35:34The #LightningNetwork introduces the concept of #payment channels. How do these channels work, and how do they enable #bitcoin to #scale while maintaining #security?
originally posted at https://stacker.news/items/878316
-
 @ 6bcc27d2:b67d296e
2025-02-07 03:06:38
@ 6bcc27d2:b67d296e
2025-02-07 03:06:38This is the test of obsidian nostr writer