-
 @ a012dc82:6458a70d
2025-03-08 10:26:25
@ a012dc82:6458a70d
2025-03-08 10:26:25The advent of Bitcoin introduced the world to a new form of digital gold, promising wealth and innovation through the marvels of blockchain technology. However, as the cryptocurrency landscape has evolved, so too have the implications of its underlying processes, particularly Bitcoin mining. In Granbury, Texas, a community has found itself at the intersection of technological advancement and environmental distress, embodying a growing concern over the real-world impacts of digital currencies. This narrative is not unique to Granbury but echoes across various locales globally, where the quest for digital wealth intersects with the fabric of everyday life, often at a cost not initially anticipated.
Table of Contents
-
The Heart of the Matter: Granbury's Plight
-
The Noise That Never Sleeps
-
A Community's Health at Stake
-
-
The Economics of Bitcoin Mining
- The Cost of Digital Wealth
-
Regulatory Responses and Community Action
- Seeking Solutions
-
The Future of Bitcoin Mining and Community Well-be …
- Sustainable Alternatives
-
Conclusion
-
FAQs
The Heart of the Matter: Granbury's Plight
Granbury, a small town in Texas, has become an unwilling host to the cacophony of Bitcoin mining. A local power plant, repurposed for the energy-intensive task of mining Bitcoin, has disrupted the lives of residents with its relentless noise. The sound, likened to the continuous roar of jet engines, penetrates the tranquility of this community, leaving in its wake sleepless nights, health issues, and a disturbed local ecosystem. This intrusion represents a broader dilemma faced by communities worldwide, where the benefits of technological progress clash with the sanctity of personal and environmental well-being.
The Noise That Never Sleeps
Cheryl Shadden, a nurse anesthetist living in Granbury, describes the noise as akin to sitting on an airport runway with jets taking off in succession. The constant hum has made simple pleasures like conversations on the back patio impossible, highlighting the intrusive nature of the mining operation. This relentless noise pollution is not just a minor inconvenience but a significant disruption to daily life, affecting everything from personal relationships to the simple enjoyment of one's home. The situation in Granbury sheds light on the often-overlooked consequences of industrial activities, prompting a reevaluation of what progress means at the expense of quality of life.
A Community's Health at Stake
The incessant din has not only stolen peace but has also been linked to physical ailments among the residents. Reports of migraines, sleep disturbances, and even wildlife fleeing the area paint a grim picture of the toll taken on the community's health and well-being. These health issues are a stark reminder of the environmental cost of our digital age, where the pursuit of innovation can sometimes lead to unforeseen consequences. The plight of Granbury's residents underscores the need for a balanced approach to technological development, one that considers the health and happiness of communities as a measure of success.
The Economics of Bitcoin Mining
Bitcoin mining, the process by which new bitcoins are entered into circulation and transactions are verified, is notoriously energy-hungry. It relies on a proof-of-work system that requires extensive computational power and, consequently, a significant amount of electricity. Texas, with its cheap energy and land, has become a global hub for these operations, attracting companies with the promise of low overhead costs. This economic boon, however, comes with its own set of challenges, as the environmental and social costs begin to surface in communities like Granbury.
The Cost of Digital Wealth
While Bitcoin mining has been lauded for its potential economic benefits, including job creation and investment, the case of Granbury reveals a darker side. The operation consumes approximately 2,100 megawatts of Texas's power supply, raising concerns about carbon and noise pollution, as well as increased utility bills for consumers. The juxtaposition of economic gain against environmental and social loss presents a complex dilemma. It raises critical questions about the sustainability of such ventures and the true cost of digital wealth in the age of cryptocurrency.
Regulatory Responses and Community Action
The situation in Granbury has sparked a dialogue on the need for regulatory oversight. Texas state law currently offers little recourse for noise pollution, with the maximum penalty for exceeding noise limits set at a mere $500 fine. This inadequacy has prompted local officials and residents to seek alternative solutions, including the construction of a sound barrier wall, which, paradoxically, has amplified the noise in some areas. The struggle for regulatory solutions reflects a broader challenge in governing emerging technologies and industries, where existing frameworks often fall short of addressing new and unforeseen impacts.
Seeking Solutions
In response to growing complaints, Marathon Digital Holdings, the company behind the Granbury mining operation, has pledged to conduct a sound study and take over full control of the mine to address community concerns. However, the effectiveness of these measures remains to be seen, and the community's frustration is palpable. This scenario highlights the importance of corporate responsibility and the need for companies to engage with and address the concerns of the communities in which they operate. It also underscores the potential for innovative solutions to mitigate the negative impacts of such operations, fostering a more harmonious relationship between industry and community.
The Future of Bitcoin Mining and Community Well-being
The case of Granbury serves as a cautionary tale of the unintended consequences of Bitcoin mining. As the cryptocurrency industry continues to grow, the balance between technological progress and environmental sustainability becomes increasingly precarious. This tension between innovation and well-being calls for a reimagined approach to technological development, one that prioritizes the health of our communities and the planet.
Sustainable Alternatives
The outcry from Granbury and similar communities across the country underscores the urgent need for sustainable mining practices. Alternatives such as proof-of-stake, a less energy-intensive consensus mechanism, offer a glimpse into a possible future where digital currencies can coexist with environmental stewardship. These alternatives not only represent a technical evolution but also a philosophical shift towards a more sustainable and equitable digital economy.
Conclusion
The story of Granbury is a microcosm of a larger debate on the impact of digital currencies on our physical world. As we venture further into the age of cryptocurrency, the challenge lies in harnessing its potential for economic growth without sacrificing the health and well-being of our communities. The digital gold rush must not lead to audible grief; instead, it should pave the way for innovations that are both economically beneficial and environmentally responsible. The journey from digital gold to a future where technology and nature harmonize requires not just technological innovation, but a collective commitment to redefining progress.
FAQs
How does Bitcoin mining affect local communities? Local communities, like Granbury, can experience noise pollution, increased electricity consumption leading to higher utility bills, potential environmental impacts due to increased energy use, and health issues among residents such as sleep disturbances and migraines.
What are the economic benefits of Bitcoin mining? Economic benefits include job creation, investment in local infrastructure, and increased demand for local services. However, these benefits often come with environmental and social costs that need to be carefully managed.
What measures are being taken to address the concerns of Granbury residents? Measures include the construction of sound barrier walls, conducting sound studies, and engaging with the community to find solutions. Companies like Marathon Digital Holdings are also taking steps to take over full control of mining operations to better address noise issues.
Are there sustainable alternatives to proof-of-work Bitcoin mining? Yes, alternatives such as proof-of-stake (PoS) are being explored and implemented in various cryptocurrencies. PoS is less energy-intensive and could potentially offer a more sustainable option for securing blockchain networks without the significant environmental impact of traditional mining.
How is the Texas government responding to the issue of Bitcoin mining noise pollution? The response includes monitoring noise levels and exploring legal and regulatory measures to manage the impact of mining operations. However, existing laws offer limited recourse, and there is ongoing discussion about the need for more effective regulations.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co/
Youtube: @thebitcoinlibertarian
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
Get Orange Pill App And Connect With Bitcoiners In Your Area. Stack Friends Who Stack Sats link: https://signup.theorangepillapp.com/opa/croxroad
Buy Bitcoin Books At Konsensus Network Store. 10% Discount With Code “21croxroad” link: https://bitcoinbook.shop?ref=21croxroad
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ d6c48950:54d57756
2025-03-08 08:17:06
@ d6c48950:54d57756
2025-03-08 08:17:06This post is going to cover some very basic habits and sanity checks that offer large returns over time whilst having a very low cost and in that theme I’m going to keep this to a condensed bullet point list.
how to get the solution faster - You solve problems every day, when you have a goal and try to achieve it, when you face a shortcoming and try and overcome it, when you have an issue and resolve it - As a habit each time you solve a problem go over your actual thoguht process, how did you solve it? - After you’ve looked critically at it ask how you could have improved it
if someones better do what they tell you - I’ve noticed a lot of people won’t take advice from people who knows better (I think because they feel if they just do what they’re told it doesn’t feel like ‘their’ accomplishment) - If someone is more credible than you and the advice they give is credible just do what you’re told
accept easy/simple solutions - Weight loss is incredibly simple, you weigh yourself daily, count your calories and maintain a deficit of 200-500kcal daily, apps automate most of the heavy lifting - As a human it’s natural to fight against simple/easy solutions to longstanding problems - “Not only has this thing been destroying my life for years but the solution is easy and something everyone already knows? the solution is the thing everyones been telling me since the problem first started?” - supress the urge to push it away and just accept the solution, even if it means your problem was mostly self inflicted and easily avoidable
log predictions - Keep a log of your predictions (I use apple numbers) then also log your confidence (55%, 65%, 75%, 85%, 95%) in each prediction and see how close you are - If you make 100 predictions at 55% confidence only 55 of them should be correct, if more are correct you’re underconfident if less are correct you’re overconfident
working harder is almost always beneficial - Despite the doomerish advice hard work and time spent working is beneficial way more than most people give it credit for - there’s probably a point at which it tops off (16hrs a day might be marginally better than 12hrs) but it’s way higher than you’d instinctively expect - Try working longer hours and harder and see how you do, in my view burnout is probably a non issue if other factors of your life (sleep, diet, exercise, stress management) are correct,
basic stuff works very well - Certain basic advice (sleep, exercise, don’t take recreational drugs, don’t drink) are not only increidlby consistent but they also have very large effect sizes, do the basic stuff before moving onto the more esoteric like nicotine patches or adderall
-
 @ d6c48950:54d57756
2025-03-08 08:16:05
@ d6c48950:54d57756
2025-03-08 08:16:05This is just a readme for my github site - this is the best way to access my blog in my opinion, it's split into several "chunks" - Layer 1, Core and central content - Layer 2, Stuff that builds upon core - Layer 3, Misc
My blog can also be found on posthaven here that has more detailed tags and a search feature - obviously my posts can also be found on nostr
-
 @ 79008e78:dfac9395
2025-03-08 07:08:11
@ 79008e78:dfac9395
2025-03-08 07:08:11Bitcoin Core: The Reference Implementation
ผู้คนจะยอมรับเงินใด ๆ เพื่อแลกเปลี่ยนกับสินค้าและบริการก็ต่อเมื่อคนนั้น ๆ เชื่อว่าเงินนี้จะมีมูลค่าในอนาคต เงินปลอมหรือเงินที่เสื่อมค่าโดยไม่คาดคิดนั้นอาจไม่สามารถใช้ได้ในอนาคต ดังนั้นทุกคนที่รับบิตคอยน์จึงมีแรงจูงใจที่แข็งแกร่งในการตรวจสอบความถูกต้องของบิตคอยน์ที่พวกเขาได้รับ ระบบของบิตคอยน์นั้นถูกออกแบบมาให้เข้าถึง, ป้องกันการปลอมแปลง, การเสื่อมค่า และปัญหาสำคัญอื่น ๆ ได้อย่างสมบูรณ์ได้ด้วยคอมพิวเตอร์ทั่วไป โดยซอฟต์แวร์ที่ให้ฟังก์ชันนี้เรียกว่า Full node ซึ่งทำหน้าที่ตรวจสอบธุรกรรมบิตคอยน์ทุกครั้งที่ได้รับการยืนยันตามกฎของระบบ นอกจากนี้ Full node ยังสามารถให้เครื่องมือและข้อมูลเพื่อทำความเข้าใจการทำงานของบิตคอยน์และสภาพปัจจุบันของเครือข่าย
ในบทนี้เอง เราจะทำการติดตั้ง Bitcoin Core ซึ่งเป็นซอฟต์แวร์ที่ผู้ใช้งาน Full node ส่วนใหญ่เลือกใช้เพื่อเป็นประตูบานแรกในการเข้าถึงระบบนิเวศของบิตคอยน์ เราจะตรวจสอบบล็อก ธุรกรรม และข้อมูลอื่น ๆ จากโหนดของคุณ ซึ่งเป็นข้อมูลที่เชื่อถือได้ (ไม่ใช่เพราะหน่วยงานทรงอำนาจกำหนดให้เป็นเช่นนั้น) แต่เป็นเพราะโหนดของคุณได้ตรวจสอบข้อมูลนั้นอย่างอิสระ ตลอดเนื้อหาที่เหลือในหนังสือเล่มนี้ เราจะใช้ Bitcoin Core เพื่อสร้างและตรวจสอบข้อมูลที่เกี่ยวข้องกับบล็อกเชนและเครือข่าย
จาก Bitcoin สู่ Bitcoin Core
บิตคอยน์เป็นโครงการโอเพ่นซอร์ส โดยซอร์สโค้ดทั้งหมดก็สามารถดาวน์โหลดและใช้งานได้ฟรีภายใต้ใบอณุญาตแบบเปิด (MIT License) นอกจากจะเป็นโอเพ่นซอร์สแล้วบิตคอยน์ยังได้รับการพัฒนาโดยชุมชนอาสาสมัครแบบเปิดกว้าง แน่นอนว่าในช่วงแรกนั้นชุมชนนี้ประกอบด้วย Satoshi Nakamoto เพียงคนเดียว แต่ภายในปี 2023 ซอร์สโค้ดของบิตคอยน์มีผู้ร่วมพัฒนามากกว่า 1,000 คน
เมื่อ Satoshi Nakamoto ได้สร้างซอฟแวร์บิตคอยน์ตัวนี้และพัฒนามันจนเกือบสมบูรณ์ก่อนแล้วจึงเผยแพร่เอกสารไวท์เปเปอร์ เขาน่าจะต้องการให้มั่นใจว่าการใช้งานจริงสามารถทำงานได้ก่อนเผยแพร่เอกสาร โดยซอฟต์แวร์เวอร์ชันแรกที่รู้จักในชื่อ "Bitcoin" นั้นได้รับการปรับปรุงและพัฒนามาอย่างมาก จนได้กลายเป็นสิ่งที่เรารู้จักกันในชื่อ Bitcoin Core และเพื่อแยกความแตกต่างจากการใช้งานอื่น ๆ Bitcoin Core เป็นซอฟต์แวร์ต้นแบบอ้างอิง (reference implementation) ของระบบบิตคอยน์ซึ่งแสดงวิธีการทำงานของแต่ละส่วนในเชิงเทคโนโลยี นอกจากนี้ Bitcoin Core รวมถึงการใช้งานฟังก์ชันทั้งหมดของบิตคอยน์ เช่น กระเป๋าเงิน เครื่องมือตรวจสอบธุรกรรมและบล็อก เครื่องมือสำหรับการสร้างบล็อก และส่วนต่าง ๆ ของการสื่อสารแบบ peer-to-peer ของบิตคอยน์

Bitcoin Development Environment
สำหรับนักพัฒนาที่ต้องการเขียนแอปพลิเคชันเกี่ยวกับบิตคอยน์ ทั้งการตั้งค่าสภาพแวดล้อมสำหรับการพัฒนาพร้อมเครื่องมือ ไลบรารี และซอฟต์แวร์สนับสนุนเป็นสิ่งสำคัญ ซึ่งเนื้อหาในบทนี้นั้นจะเป็นเรื่องทางเทคนิคอลค่อนข้างเยอะ ในบทนี้เราจะอธิบายขั้นตอนการตั้งค่าอย่างละเอียด หากคุณพบว่าเนื้อหานี้ซับซ้อนเกินไป (และไม่ได้ต้องการตั้งค่าสภาพแวดล้อมสำหรับการพัฒนาจริง ๆ) คุณสามารถข้ามไปยังบทถัดไปที่มีเนื้อหาน้อยทางเทคนิคกว่าได้
มาคอมไพล์ Bitcoin core จากซอร์สโค้ดกันเถอะ !!
ซอร์สโค้ดทั้งหมดของ BItcoin Core นั้นสามารถดาวน์โหลดได้ในรูปแบบไฟล์อาร์ไคฟ์หรือโดยการโคลนที่เก็บซอร์สโค้ดจาก GitHub โดยตรง บนหน้าดาวน์โหลดของ Bitcoin Core ให้เลือกเวอร์ชันล่าสุดและดาวน์โหลดไฟล์อัดบีบของซอร์สโค้ด หรือใช้คำสั่ง Git เพื่อสร้างสำเนาซอร์สโค้ดบนเครื่องของคุณจากหน้า GitHub ของ Bitcoin
TIP: ในตัวอย่างหลาย ๆ ส่วนของบทนี้ เราจะใช้ อินเทอร์เฟซบรรทัดคำสั่ง (Command-Line Interface - CLI) ของระบบปฏิบัติการ หรือที่เรียกว่า "shell" ซึ่งสามารถเข้าถึงได้ผ่านแอปพลิเคชัน terminal โดย shell จะแสดง พรอมต์ (prompt) เพื่อรอรับคำสั่งที่คุณพิมพ์ จากนั้นจะแสดงผลลัพธ์ออกมาแล้วรอรับคำสั่งถัดไป
TIP จากหลาม: แบบง่าย ๆ ก็คือไม่ต้องพิมพ์ $ และถ้าพิมพ์จบหนึ่งคำสั่งก็กด enter ซ่ะด้วย
ขั้นตอนในการลง bitcoin core มีดังนี้:
- สั่ง git clone เพื่อทำการสร้างสำเนาของซอร์สโค้ดลงในเครื่องของเรา ``` $ git clone https://github.com/bitcoin/bitcoin.git Cloning into 'bitcoin'... remote: Enumerating objects: 245912, done. remote: Counting objects: 100% (3/3), done. remote: Compressing objects: 100% (2/2), done. remote: Total 245912 (delta 1), reused 2 (delta 1), pack-reused 245909 Receiving objects: 100% (245912/245912), 217.74 MiB | 13.05 MiB/s, done. Resolving deltas: 100% (175649/175649), done.
```
TIP: Git เป็นระบบควบคุมเวอร์ชันแบบกระจายที่ใช้กันอย่างแพร่หลายและเป็นส่วนสำคัญในเครื่องมือของนักพัฒนาซอฟต์แวร์ คุณอาจจำเป็นต้องติดตั้งคำสั่ง git หรือส่วนต่อประสานกราฟิก (GUI) สำหรับ Git บนระบบปฏิบัติการของคุณ หากยังไม่มี
- เมื่อการโคลน Git เสร็จสมบูรณ์แล้ว คุณจะมีสำเนาท้องถิ่นครบถ้วนของที่เก็บซอร์สโค้ดในไดเรกทอรี bitcoin ให้เปลี่ยนไปยังไดเรกทอรีนี้โดยใช้คำสั่ง cd:
``` $ cd bitcoin
3. เลือก version ของ bitcoin core: โดยค่าเริ่มต้น สำเนาจองเราจะซิงโครไนซ์กับโค้ดล่าสุด ซึ่งอาจเป็นเวอร์ชันที่ไม่เสถียรหรือเบต้าของ Bitcoin ก่อนที่จะคอมไพล์โค้ด ให้เลือกเวอร์ชันเฉพาะโดยการตรวจสอบ (checkout) แท็กของการปล่อย (release tag) ซึ่งจะซิงโครไนซ์สำเนาท้องถิ่นกับสแนปช็อตของที่เก็บซอร์สโค้ดที่ระบุด้วยแท็ก แท็กเหล่านี้ถูกใช้งานโดยนักพัฒนาเพื่อระบุเวอร์ชันของโค้ดตามหมายเลขเวอร์ชัน ซึ่งทำได้โดยใช้คำสั่ง git tag$ git tag v0.1.5 v0.1.6test1 v0.10.0 ... v0.11.2 v0.11.2rc1 v0.12.0rc1 v0.12.0rc2 ...รายการแท็กจะแสดงทุกเวอร์ชันที่ปล่อยออกมา โดยทั่วไป release candidates (เวอร์ชันทดสอบ) จะมีต่อท้ายว่า "rc" ส่วนเวอร์ชันเสถียรที่ใช้งานในระบบ production จะไม่มีต่อท้ายอะไรเลย จากรายการด้านบน ให้เลือกเวอร์ชันที่สูงสุด ซึ่งในขณะที่เขียนบทความนี้คือ v24.0.1 เพื่อซิงโครไนซ์โค้ดท้องถิ่นกับเวอร์ชันนี้ ให้ใช้คำสั่ง:$ git checkout v24.0.1 Note: switching to 'v24.0.1'.```
จากนั้นสั่ง git status เพื่อเช็คเวอร์ชัน
Configuring the Bitcoin Core Build
ในโค้ดของบิตคอยน์ที่เราได้ดาวน์โหลดมาในหัวข้อก่อนหน้านั้น มีเอกสารประกอบอยู่หลายไฟล์ โดยคุณสามารถดูเอกสารหลักได้จากไฟล์ README.md ในไดเรกทอรี bitcoin ในบทนี้ เราจะสร้าง daemon (เซิร์ฟเวอร์) ของ Bitcoin Core ซึ่งรู้จักกันในชื่อ bitcoind บน Linux (หรือระบบที่คล้ายกับ Unix) โดยให้ตรวจสอบคำแนะนำสำหรับการคอมไพล์ bitcoind แบบบรรทัดคำสั่งบนแพลตฟอร์มของคุณโดยอ่านไฟล์ doc/build-unix.md นอกจากนี้ ยังมีคำแนะนำสำหรับระบบอื่น ๆ ในไดเรกทอรี doc เช่น build-windows.md สำหรับ Windows จนถึงขณะนี้ คำแนะนำมีให้สำหรับ Android, FreeBSD, NetBSD, OpenBSD, macOS (OSX), Unix
หลังจากนั้นคุณควรตรวจสอบความต้องการเบื้องต้นในการสร้าง (build pre-requisites) ซึ่งระบุไว้ในส่วนแรกของเอกสารการสร้าง สิ่งเหล่านี้คือไลบรารีที่ต้องมีอยู่ในระบบของคุณก่อนที่คุณจะเริ่มคอมไพล์ Bitcoin หากมีไลบรารีที่จำเป็นหายไป กระบวนการสร้างจะล้มเหลวและแสดงข้อผิดพลาด หากเกิดปัญหานี้เพราะคุณพลาด pre-requisite คุณสามารถติดตั้งไลบรารีที่ขาดหายไปแล้วดำเนินการสร้างต่อจากจุดที่ค้างไว้
สมมุติว่า pre-requisite ถูกติดตั้งแล้ว ให้เริ่มกระบวนการสร้างโดยการสร้างชุดสคริปต์สำหรับการสร้างด้วยการรันสคริปต์ autogen.sh:
``` $ ./autogen.sh libtoolize: putting auxiliary files in AC_CONFIG_AUX_DIR, 'build-aux'. libtoolize: copying file 'build-aux/ltmain.sh' libtoolize: putting macros in AC_CONFIG_MACRO_DIRS, 'build-aux/m4'. ... configure.ac:58: installing 'build-aux/missing' src/Makefile.am: installing 'build-aux/depcomp' parallel-tests: installing 'build-aux/test-driver'
``` สคริปต์ autogen.sh นี้จะสร้างชุดสคริปต์ที่กำหนดค่าอัตโนมัติที่จะตรวจสอบระบบของคุณเพื่อค้นหาการตั้งค่าที่ถูกต้องและตรวจสอบให้แน่ใจว่ามีไลบรารีที่จำเป็นสำหรับการคอมไพล์โค้ด โดยสคริปต์ที่สำคัญที่สุดในสคริปต์เหล่านี้คือสคริปต์ configure ซึ่งมีตัวเลือกต่าง ๆ สำหรับการปรับแต่งกระบวนการสร้าง
ใช้ flag --help เพื่อดูตัวเลือกทั้งหมด:
`` $ ./configure --helpconfigure' configures Bitcoin Core 24.0.1 to adapt to many kinds of systems. Usage: ./configure [OPTION]... [VAR=VALUE]... ... Optional Features: --disable-option-checking ignore unrecognized --enable/--with options --disable-FEATURE do not include FEATURE (same as --enable-FEATURE=no) --enable-FEATURE[=ARG] include FEATURE [ARG=yes] --enable-silent-rules less verbose build output (undo: "make V=1") --disable-silent-rules verbose build output (undo: "make V=0") ...```
สคริปต์ configure ช่วยให้คุณสามารถเปิดหรือปิดคุณสมบัติบางอย่างของ bitcoind ผ่านการใช้ flag --enable-FEATURE และ --disable-FEATURE โดยที่ FEATURE แทนชื่อคุณสมบัติที่ระบุในข้อความช่วยเหลือ ในบทนี้ เราจะสร้าง bitcoind ด้วยคุณสมบัติตั้งต้นทั้งหมด โดยไม่ใช้ flag การกำหนดค่าเพิ่มเติม แต่คุณควรตรวจสอบตัวเลือกเหล่านี้เพื่อเข้าใจว่ามีคุณสมบัติเพิ่มเติมอะไรบ้าง หากคุณอยู่ในสภาพแวดล้อมทางการศึกษา ห้องปฏิบัติการคอมพิวเตอร์ หรือมีข้อจำกัดในการติดตั้งโปรแกรม คุณอาจต้องติดตั้งแอปพลิเคชันไว้ในไดเรกทอรี home (เช่นโดยใช้ flag --prefix=$HOME)
ตัวเลือกที่มีประโยชน์สำหรับการกำหนดค่า
- --prefix=$HOME: เปลี่ยนตำแหน่งการติดตั้งเริ่มต้น (ซึ่งโดยปกติคือ /usr/local/) ให้เป็นไดเรกทอรี home ของคุณ หรือเส้นทางที่คุณต้องการ
- --disable-wallet: ใช้เพื่อปิดการใช้งานฟังก์ชัน wallet แบบอ้างอิง
- --with-incompatible-bdb: หากคุณกำลังสร้าง wallet ให้ยอมรับการใช้ไลบรารี Berkeley DB เวอร์ชันที่ไม่เข้ากันได้
- --with-gui=no: ไม่สร้างส่วนติดต่อผู้ใช้แบบกราฟิก (GUI) ซึ่งต้องใช้ไลบรารี Qt โดยตัวเลือกนี้จะสร้างเฉพาะเซิร์ฟเวอร์และ Bitcoin Core แบบ commandline เท่านั้น
```
ต่อไป ให้รันสคริปต์ configure เพื่อให้ระบบตรวจสอบไลบรารีที่จำเป็นทั้งหมดและสร้างสคริปต์สำหรับการสร้างที่ปรับแต่งให้ตรงกับระบบของคุณ:$ ./configure checking for pkg-config... /usr/bin/pkg-config checking pkg-config is at least version 0.9.0... yes checking build system type... x86_64-pc-linux-gnu checking host system type... x86_64-pc-linux-gnu checking for a BSD-compatible install... /usr/bin/install -c ... [many pages of configuration tests follow] ... ```หากทุกอย่างดำเนินไปด้วยดี คำสั่ง configure จะสิ้นสุดด้วยการสร้างสคริปต์การสร้างที่ปรับแต่งให้กับระบบของคุณ แต่หากมีไลบรารีที่หายไปหรือเกิดข้อผิดพลาด คำสั่ง configure จะหยุดและแสดงข้อผิดพลาดแทนที่จะสร้างสคริปต์ในกรณีที่เกิดข้อผิดพลาดขึ้น สาเหตุที่พบบ่อยคือการขาดหายหรือความไม่เข้ากันของไลบรารี ให้ตรวจสอบเอกสารการสร้างอีกครั้งและติดตั้ง pre-requisite ที่ขาดไป จากนั้นรัน configure อีกครั้งเพื่อดูว่าปัญหานั้นได้รับการแก้ไขแล้วหรือไม่
การสร้าง Executable ของ Bitcoin Core
ต่อไป คุณจะทำการคอมไพล์ซอร์สโค้ด กระบวนการนี้อาจใช้เวลาถึงหนึ่งชั่วโมง ขึ้นอยู่กับความเร็วของ CPU และหน่วยความจำที่มีอยู่ หากเกิดข้อผิดพลาด หรือการคอมไพล์ถูกขัดจังหวะ คุณสามารถดำเนินการต่อได้โดยการพิมพ์คำสั่ง make อีกครั้ง
พิมพ์ make เพื่อเริ่มคอมไพล์แอปพลิเคชันที่สามารถรันได้: ``` $ make Making all in src CXX bitcoind-bitcoind.o CXX libbitcoin_node_a-addrdb.o CXX libbitcoin_node_a-addrman.o CXX libbitcoin_node_a-banman.o CXX libbitcoin_node_a-blockencodings.o CXX libbitcoin_node_a-blockfilter.o [... many more compilation messages follow ...]
```
บนระบบที่มีความเร็วและมี CPU หลายคอร์ คุณอาจต้องการตั้งค่าจำนวนงานคอมไพล์แบบขนาน (parallel compile jobs) เช่น การใช้คำสั่ง make -j 2 จะใช้สองคอร์หากมีอยู่ หากทุกอย่างดำเนินไปด้วยดี Bitcoin Core จะถูกคอมไพล์เรียบร้อยแล้ว คุณควรรันชุดการทดสอบหน่วย (unit test suite) ด้วยคำสั่ง make check เพื่อให้แน่ใจว่าไลบรารีที่ลิงค์เข้าด้วยกันไม่มีข้อผิดพลาดอย่าง ขั้นตอนสุดท้ายคือการติดตั้ง executable ต่าง ๆ ลงในระบบของคุณโดยใช้คำสั่ง make install ซึ่งอาจมีการร้องขอรหัสผ่านของผู้ใช้เนื่องจากขั้นตอนนี้ต้องการสิทธิ์ผู้ดูแลระบบ: ``` $ make check && sudo make install Password: Making install in src ../build-aux/install-sh -c -d '/usr/local/lib' libtool: install: /usr/bin/install -c bitcoind /usr/local/bin/bitcoind libtool: install: /usr/bin/install -c bitcoin-cli /usr/local/bin/bitcoin-cli libtool: install: /usr/bin/install -c bitcoin-tx /usr/local/bin/bitcoin-tx ...
```
การติดตั้งเริ่มต้นของ bitcoind จะอยู่ในไดเรกทอรี /usr/local/bin โดยคุณสามารถตรวจสอบว่า Bitcoin Core ถูกติดตั้งเรียบร้อยแล้วโดยใช้คำสั่งเพื่อตรวจสอบตำแหน่งของ executable ดังนี้:
$ which bitcoind /usr/local/bin/bitcoind $ which bitcoin-cli /usr/local/bin/bitcoin-cliมาลองรัน Bitcoin node กันเถอะ
อย่างที่ได้กล่าวในบทก่อนหน้า เครือข่ายแบบเพียร์ทูเพียร์ของบิตคอยน์ประกอบด้วยเครือข่าย "โหนด" ซึ่งส่วนใหญ่รันโดยบุคคลและธุรกิจบางแห่งที่ให้บริการ ผู้ที่รันโหนดบิตคอยน์จะมีมุมมองที่ตรงและน่าเชื่อถือเกี่ยวกับบล๊อกเชนของบิตคอยน์พร้อมสำเนาข้อมูลบิตคอยน์ที่ใช้จ่ายได้ทั้งหมดซึ่งได้รับการตรวจสอบอย่างอิสระโดยระบบของตนเอง การรันโหนดทำให้คุณไม่ต้องพึ่งบุคคลที่สามในการตรวจสอบธุรกรรม นอกจากนี้การใช้โหนดบิตคอยน์เพื่อตรวจสอบธุรกรรมที่ได้รับในกระเป๋าเงินของคุณ ยังช่วยให้คุณมีส่วนร่วมในเครือข่ายบิตคอยน์และช่วยทำให้เครือข่ายมีความแข็งแกร่งมากขึ้นอีกด้วย
การรันโหนดต้องดาวน์โหลดและประมวลผลข้อมูลมากกว่า 500 GB ในช่วงเริ่มแรก และประมาณ 400 MB ของธุรกรรม Bitcoin ต่อวัน ตัวเลขเหล่านี้เป็นของปี 2023 และอาจเพิ่มขึ้นในอนาคต หากคุณปิดโหนดหรือหลุดจากอินเทอร์เน็ตเป็นเวลาหลายวัน โหนดของคุณจะต้องดาวน์โหลดข้อมูลที่พลาดไป ตัวอย่างเช่น หากคุณปิด Bitcoin Core เป็นเวลา 10 วัน คุณจะต้องดาวน์โหลดประมาณ 4 GB ในครั้งถัดไปที่คุณเริ่มใช้งาน
ขึ้นอยู่กับการเลือกของคุณว่าจะทำดัชนีธุรกรรมทั้งหมดและเก็บสำเนาบล๊อกเชนแบบเต็ม คุณอาจต้องใช้พื้นที่ดิสก์มาก - อย่างน้อย 1 TB หากคุณวางแผนจะรัน Bitcoin Core เป็นเวลาหลายปี โดยค่าเริ่มต้นโหนดบิตคอยน์ยังส่งธุรกรรมและบล็อกไปยังโหนดอื่น ๆ (เรียกว่า "เพียร์") ซึ่งจะใช้แบนด์วิดท์อัปโหลดอินเทอร์เน็ต หากการเชื่อมต่ออินเทอร์เน็ตของคุณมีขีดจำกัด มีขีดจำกัดการใช้ข้อมูลต่ำ หรือคิดค่าบริการตามข้อมูล (เมตเตอร์) คุณไม่ควรรันโหนดบิตคอยน์บนระบบนั้น หรือรันโดยจำกัดแบนด์วิดท์ (ดู การกำหนดค่าโหนด Bitcoin Core) คุณอาจเชื่อมต่อโหนดของคุณแทนไปยังเครือข่ายทางเลือก เช่น ผู้ให้บริการข้อมูลดาวเทียมฟรีอย่าง Blockstream Satellite
Tip: Bitcoin Core เก็บสำเนาบล๊อกเชนแบบเต็ม (ตามค่าเริ่มต้น ) พร้อมธุรกรรมเกือบทั้งหมดที่เคยได้รับการยืนยันบนเครือข่าย Bitcoin ตั้งแต่เริ่มต้นในปี 2009 ชุดข้อมูลนี้มีขนาดหลายร้อย GB และจะถูกดาวน์โหลดเพิ่มขึ้นทีละน้อยในช่วงหลายชั่วโมงหรือหลายวัน ขึ้นอยู่กับความเร็ว CPU และการเชื่อมต่ออินเทอร์เน็ตของคุณ Bitcoin Core จะไม่สามารถประมวลผลธุรกรรมหรืออัปเดตยอดคงเหลือของบัญชีจนกว่าชุดข้อมูล blockchain จะดาวน์โหลดเสร็จสมบูรณ์ ตรวจสอบให้แน่ใจว่าคุณมีพื้นที่ดิสก์ แบนด์วิดท์ และเวลาเพียงพอในการซิงโครไนซ์เริ่มแรก คุณสามารถกำหนดค่า Bitcoin Core เพื่อลดขนาด blockchain โดยการทิ้งบล็อกเก่า แต่โปรแกรมยังคงดาวน์โหลดชุดข้อมูลทั้งหมด
TIPจากหลาม agian: ซื้อ NVMe SSD 2TB เป็นอย่างต่ำซ่ะ m.2 ได้ยิ่งดีเลยจ้า
แม้ว่าจะมีข้อกำหนดด้านทรัพยากรเหล่านี้ แต่มีผู้คนหลายพันรายที่รันโหนด Bitcoin บางคนรันบนระบบง่าย ๆ อย่าง Raspberry Pi (คอมพิวเตอร์ราคา 35 เหรียญสหรัฐที่มีขนาดเท่ากับกล่องบุหรี่)
ทำไมคุณถึงอยากรันโหนด? นี่คือเหตุผลที่พบบ่อยที่สุด:
- คุณไม่ต้องการพึ่งบุคคลที่สามในการตรวจสอบธุรกรรมที่คุณได้รับ
- คุณไม่ต้องการเปิดเผยให้บุคคลที่สามรู้ว่าธุรกรรมใดเป็นของกระเป๋าเงินคุณ
- คุณกำลังพัฒนาซอฟต์แวร์ Bitcoin และต้องการพึ่งโหนด Bitcoin เพื่อเข้าถึงเครือข่ายและ blockchain ผ่าน API
- คุณกำลังสร้างแอปพลิเคชันที่ต้องตรวจสอบธุรกรรมตามกฎฉันทามติของ Bitcoin โดยทั่วไป บริษัทซอฟต์แวร์ Bitcoin มักจะรันโหนดหลายโหนด
- คุณต้องการสนับสนุน Bitcoin การรันโหนดที่คุณใช้ตรวจสอบธุรกรรมที่ได้รับในกระเป๋าเงินจะช่วยทำให้เครือข่ายมีความแข็งแกร่งมากขึ้น
หากคุณกำลังอ่านหนังสือเล่มนี้และสนใจความปลอดภัยที่เข้มงวด ความเป็นส่วนตัวที่เหนือกว่า หรือการพัฒนาซอฟต์แวร์ Bitcoin คุณควรรันโหนดของตัวเอง
การกำหนดค่าโหนด Bitcoin Core
Bitcoin Core จะค้นหาไฟล์การกำหนดค่าในไดเรกทอรีข้อมูลทุกครั้งที่เริ่มทำงาน ในส่วนนี้เราจะตรวจสอบตัวเลือกการกำหนดค่าต่าง ๆ และตั้งค่าไฟล์การกำหนดค่า
เพื่อค้นหาไฟล์การกำหนดค่า ให้รัน bitcoind -printtoconsole ในเทอร์มินัลของคุณ และดูบรรทัดแรก ๆ:
$ bitcoind -printtoconsole 2023-01-28T03:21:42Z Bitcoin Core version v24.0.1 2023-01-28T03:21:42Z Using the 'x86_shani(1way,2way)' SHA256 implementation 2023-01-28T03:21:42Z Using RdSeed as an additional entropy source 2023-01-28T03:21:42Z Using RdRand as an additional entropy source 2023-01-28T03:21:42Z Default data directory /home/harding/.bitcoin 2023-01-28T03:21:42Z Using data directory /home/harding/.bitcoin 2023-01-28T03:21:42Z Config file: /home/harding/.bitcoin/bitcoin.conf ... [a lot more debug output] ...tatatipจากหลามอีกครั้ง: สังเกตเห็นหรือไม่ว่าในตัวอย่างนี้ Bitcoin Core กำลังชี้ไปที่ไฟล์การกำหนดค่าที่ไดเรกทอรี /home/harding/.bitcoin/bitcoin.conf ซึ่งจะแตกต่างกันไปขึ้นอยู่กับผู้ใช้และระบบปฏิบัติการ
คุณสามารถกด Ctrl-C เพื่อปิดโหนดหลังจากที่ระบุตำแหน่งไฟล์การกำหนดค่า โดยปกติไฟล์การกำหนดค่าจะอยู่ในไดเรกทอรี .bitcoin ภายใต้โฮมไดเรกทอรีของผู้ใช้ เปิดไฟล์ configuration ด้วยโปรแกรมแก้ไขได้ตามที่คุณชอบ
Bitcoin Core มีตัวเลือกการกำหนดค่ามากกว่า 100 ตัวเลือกที่สามารถปรับเปลี่ยนพฤติกรรมของโหนดเครือข่าย การจัดเก็บบล๊อกเชน และแง่มุมอื่น ๆ ของการทำงาน เพื่อดูรายการตัวเลือก ให้รัน bitcoind --help:
$ bitcoind --help Bitcoin Core version v24.0.1 Usage: bitcoind [options] Start Bitcoin Core Options: -? Print this help message and exit -alertnotify=<cmd> Execute command when an alert is raised (%s in cmd is replaced by message) ... [many more options]นี่คือตัวเลือกที่บางประการที่คุณสามารถตั้งในไฟล์ configuration หรือเป็นพารามิเตอร์บรรทัดคำสั่งสำหรับ bitcoind:
- alertnotify: เรียกใช้คำสั่งหรือสคริปต์เพื่อส่งการแจ้งเตือนฉุกเฉินไปยังเจ้าของโหนดนี้
- conf: ตำแหน่งทางเลือกสำหรับไฟล์ configuration เมื่อใช้เป็นพารามิเตอร์ cli สำหรับ bitcoind เท่านั้น เนื่องจากไม่สามารถอยู่ในไฟล์ configuration ที่มันอ้างถึงได้
- datadir: เลือกไดเรกทอรีและระบบไฟล์สำหรับจัดเก็บข้อมูลบล๊อกเชนตามค่าเริ่มต้นนี้คือไดเรกทอรีย่อย .bitcoin ในไดเรกทอรีโฮมของคุณ ขึ้นอยู่กับการกำหนดค่า สามารถใช้พื้นที่ตั้งแต่ประมาณ 10 GB ถึงเกือบ 1 TB ณ ขณะนี้ คาดว่าขนาดสูงสุดจะเพิ่มขึ้นหลายร้อย GB ต่อปี
- prune: ลดความต้องการพื้นที่ดิสก์บล๊อกเชนลงเหลือกี่เมกะไบต์โดยการลบบล็อกเก่า ใช้สำหรับโหนดที่มีทรัพยากรจำกัดซึ่งไม่สามารถบรรจุบล๊อกเชนแบบเต็มได้ ส่วนอื่น ๆ ของระบบจะใช้พื้นที่ดิสก์อื่นที่ไม่สามารถตัดทอนได้ ดังนั้นคุณยังคงต้องมีพื้นที่อย่างน้อยตามที่ระบุในตัวเลือก datadir
- txindex: รักษาดัชนีของธุรกรรมทั้งหมด ช่วยให้คุณสามารถดึงธุรกรรมใด ๆ โดยใช้ ID ของมันได้โดยโปรแกรม โดยที่บล็อกที่มีธุรกรรมนั้นยังไม่ถูกตัดทอน
- dbcache: ขนาดของแคช UTXO ค่าเริ่มต้นคือ 450 เมบิไบต์ (MiB) เพิ่มขนาดนี้บนฮาร์ดแวร์ระดับสูงเพื่ออ่านและเขียนจากดิสก์น้อยลง หรือลดขนาดลงบนฮาร์ดแวร์ระดับต่ำเพื่อประหยัดหน่วยความจำโดยยอมให้ใช้ดิสก์บ่อยขึ้น
- blocksonly: ลดการใช้แบนด์วิดท์โดยการรับเฉพาะบล็อกของธุรกรรมที่ได้รับการยืนยันจากเพียร์ แทนที่จะส่งต่อธุรกรรมที่ยังไม่ได้รับการยืนยัน
- maxmempool: จำกัดพูลหน่วยความจำของธุรกรรมเป็นกี่เมกะไบต์ ใช้เพื่อลดการใช้หน่วยความจำบนโหนดที่มีหน่วยความจำจำกัด
ดัชนีฐานข้อมูลธุรกรรมและตัวเลือก txindex
ตามค่าเริ่มต้น Bitcoin Core จะสร้างฐานข้อมูลที่มีเพียงธุรกรรมที่เกี่ยวข้องกับกระเป๋าเงินของผู้ใช้เท่านั้น หากคุณต้องการสามารถเข้าถึงธุรกรรมใด ๆ ด้วยคำสั่งเช่น getrawtransaction คุณจะต้องกำหนดค่า Bitcoin Core ให้สร้างดัชนีธุรกรรมแบบสมบูรณ์ ซึ่งสามารถทำได้ด้วยตัวเลือก txindex โดยตั้ง txindex=1 ในไฟล์การกำหนดค่า Bitcoin Core หากคุณไม่ได้ตั้งตัวเลือกนี้ตั้งแต่แรกและต่อมาตั้งเป็นการทำดัชนีแบบเต็ม คุณจะต้องรอให้มันสร้างดัชนีใหม่
ตัวอย่างการกำหนดค่าโหนดดัชนีแบบเต็มแสดงวิธีที่คุณอาจรวมตัวเลือกก่อนหน้านี้กับโหนดที่มีดัชนีแบบเต็ม โดยทำงานเป็นแบ็กเอนด์ API สำหรับแอปพลิเคชัน bitcoin
ตัวอย่างที่ 1. การกำหนดค่าโหนดดัชนีแบบเต็ม
alertnotify=myemailscript.sh "Alert: %s" datadir=/lotsofspace/bitcoin txindex=1ตัวอย่างที่ 2. การกำหนดค่าระบบที่มีทรัพยากรจำกัด
alertnotify=myemailscript.sh "Alert: %s" blocksonly=1 prune=5000 dbcache=150 maxmempool=150หลังจากที่คุณแก้ไขไฟล์การกำหนดค่าและตั้งตัวเลือกที่ดีที่สุดตามความต้องการของคุณ คุณสามารถทดสอบ bitcoind ด้วยการกำหนดค่านี้ รัน Bitcoin Core ด้วยตัวเลือก printtoconsole เพื่อรันที่ foreground พร้อมแสดงผลลัพธ์ที่คอนโซล:
$ bitcoind -printtoconsole 2023-01-28T03:43:39Z Bitcoin Core version v24.0.1 2023-01-28T03:43:39Z Using the 'x86_shani(1way,2way)' SHA256 implementation 2023-01-28T03:43:39Z Using RdSeed as an additional entropy source 2023-01-28T03:43:39Z Using RdRand as an additional entropy source 2023-01-28T03:43:39Z Default data directory /home/harding/.bitcoin 2023-01-28T03:43:39Z Using data directory /lotsofspace/bitcoin 2023-01-28T03:43:39Z Config file: /home/harding/.bitcoin/bitcoin.conf 2023-01-28T03:43:39Z Config file arg: [main] blockfilterindex="1" 2023-01-28T03:43:39Z Config file arg: [main] maxuploadtarget="1000" 2023-01-28T03:43:39Z Config file arg: [main] txindex="1" 2023-01-28T03:43:39Z Setting file arg: wallet = ["msig0"] 2023-01-28T03:43:39Z Command-line arg: printtoconsole="" 2023-01-28T03:43:39Z Using at most 125 automatic connections 2023-01-28T03:43:39Z Using 16 MiB out of 16 MiB requested for signature cache 2023-01-28T03:43:39Z Using 16 MiB out of 16 MiB requested for script execution 2023-01-28T03:43:39Z Script verification uses 3 additional threads 2023-01-28T03:43:39Z scheduler thread start 2023-01-28T03:43:39Z [http] creating work queue of depth 16 2023-01-28T03:43:39Z Using random cookie authentication. 2023-01-28T03:43:39Z Generated RPC cookie /lotsofspace/bitcoin/.cookie 2023-01-28T03:43:39Z [http] starting 4 worker threads 2023-01-28T03:43:39Z Using wallet directory /lotsofspace/bitcoin/wallets 2023-01-28T03:43:39Z init message: Verifying wallet(s)… 2023-01-28T03:43:39Z Using BerkeleyDB version Berkeley DB 4.8.30 2023-01-28T03:43:39Z Using /16 prefix for IP bucketing 2023-01-28T03:43:39Z init message: Loading P2P addresses… 2023-01-28T03:43:39Z Loaded 63866 addresses from peers.dat 114ms [... more startup messages ...]คุณสามารถกด Ctrl-C เพื่อหยุดกระบวนการเมื่อคุณพอใจว่ากำลังโหลดการตั้งค่าที่ถูกต้องและทำงานตามที่คาดหวัง
เพื่อรัน Bitcoin Core ที่พื้นหลังเป็นโพรเซส ให้เริ่มด้วยตัวเลือก daemon เช่น bitcoind -daemon
เพื่อตรวจสอบความคืบหน้าและสถานะการทำงานของโหนด Bitcoin ให้เริ่มในโหมด daemon แล้วใช้คำสั่ง bitcoin-cli getblockchaininfo:
``` $ bitcoin-cli getblockchaininfo
{ "chain": "main", "blocks": 0, "headers": 83999, "bestblockhash": "[...]19d6689c085ae165831e934ff763ae46a2a6c172b3f1b60a8ce26f", "difficulty": 1, "time": 1673379796, "mediantime": 1231006505, "verificationprogress": 3.783041623201835e-09, "initialblockdownload": true, "chainwork": "[...]000000000000000000000000000000000000000000000100010001", "size_on_disk": 89087, "pruned": false, "warnings": "" }
```
นี่แสดงโหนดที่มีความสูงของ blockchain เป็น 0 บล็อก และ 83,999 เฮดเดอร์ โหนดจะดึงเฮดเดอร์ของบล็อกจากเพียร์ของตนก่อนเพื่อค้นหา blockchain ที่มีหลักฐานการทำงานมากที่สุด จากนั้นจึงดำเนินการดาวน์โหลดบล็อกเต็มโดยตรวจสอบความถูกต้องไปพร้อมกัน
เมื่อคุณพอใจกับตัวเลือกการกำหนดค่าที่เลือก คุณควรเพิ่ม Bitcoin Core ลงในสคริปต์เริ่มต้นของระบบปฏิบัติการ เพื่อให้มันทำงานอย่างต่อเนื่องและรีสตาร์ทเมื่อระบบปฏิบัติการรีสตาร์ท คุณจะพบสคริปต์เริ่มต้นตัวอย่างสำหรับระบบปฏิบัติการต่าง ๆ ในไดเรกทอรีซอร์สของ Bitcoin Core ภายใต้ contrib/init และไฟล์ README.md ที่แสดงว่าระบบใดใช้สคริปต์ใด
Bitcoin Core API
Bitcoin Core ใช้อินเทอร์เฟซ JSON-RPC ซึ่งสามารถเข้าถึงได้โดยใช้เครื่องมืออย่าง bitcoin-cli ซึ่งช่วยให้เราสามารถทดลองใช้งานความสามารถต่างๆ แบบโต้ตอบได้ ซึ่งความสามารถเหล่านี้ยังสามารถใช้งานได้ผ่านทาง API ในรูปแบบโปรแกรม เพื่อเริ่มต้น ให้เรียกใช้คำสั่ง help เพื่อดูรายการคำสั่ง Bitcoin Core RPC ที่มีอยู่:
$ bitcoin-cli help +== Blockchain == getbestblockhash getblock "blockhash" ( verbosity ) getblockchaininfo ... walletpassphrase "passphrase" timeout walletpassphrasechange "oldpassphrase" "newpassphrase" walletprocesspsbt "psbt" ( sign "sighashtype" bip32derivs finalize )คำสั่งแต่ละรายการอาจต้องการพารามิเตอร์หลายตัว เพื่อรับความช่วยเหลือเพิ่มเติม คำอธิบายโดยละเอียด และข้อมูลเกี่ยวกับพารามิเตอร์ต่างๆ ให้เพิ่มชื่อคำสั่งหลังคำว่า help ตัวอย่างเช่น เพื่อดูความช่วยเหลือเกี่ยวกับคำสั่ง RPC getblockhash: ``` $ bitcoin-cli help getblockhash getblockhash height Returns hash of block in best-block-chain at height provided. Arguments: 1. height (numeric, required) The height index Result: "hex" (string) The block hash Examples:
bitcoin-cli getblockhash 1000 curl --user myusername --data-binary '{"jsonrpc": "1.0", "id": "curltest", "method": "getblockhash", "params": [1000]}' -H 'content-type: text/plain;' http://127.0.0.1:8332/ ``` ในส่วนท้ายของข้อมูลคำสั่ง help คุณจะเห็นตัวอย่างสองตัวอย่างของคำสั่ง RPC ซึ่งใช้ตัวช่วย bitcoin-cli หรือ HTTP client curl ตัวอย่างเหล่านี้แสดงให้เห็นว่าคุณอาจเรียกใช้คำสั่งได้อย่างไร ลองคัดลอกตัวอย่างแรกและดูผลลัพธ์:
$ bitcoin-cli getblockhash 1000 00000000c937983704a73af28acdec37b049d214adbda81d7e2a3dd146f6ed09ผลลัพธ์คือแฮชของบล็อก ซึ่งจะอธิบายในรายละเอียดเพิ่มเติมในบทต่อไป แต่ในตอนนี้ คำสั่งนี้ควรให้ผลลัพธ์เหมือนกันบนระบบของคุณ ซึ่งแสดงให้เห็นว่าโหนด Bitcoin Core ของคุณกำลังทำงาน กำลังรับคำสั่ง และมีข้อมูลเกี่ยวกับบล็อก 1,000 ที่จะส่งกลับมาให้คุณ
การรับข้อมูลสถานะของ Bitcoin Core
Bitcoin Core ให้รายงานสถานะเกี่ยวกับโมดูลต่างๆ ผ่านอินเตอร์เฟส JSON-RPC คำสั่งที่สำคัญที่สุดรวมถึง getblockchaininfo, getmempoolinfo, getnetworkinfo และ getwalletinfo
คำสั่ง RPC getblockchaininfo ของ Bitcoin ได้ถูกแนะนำไปก่อนหน้านี้แล้ว คำสั่ง getnetworkinfo แสดงข้อมูลพื้นฐานเกี่ยวกับสถานะของโหนดเครือข่าย Bitcoin ใช้ bitcoin-cli เพื่อรันคำสั่งนี้:
$ bitcoin-cli getnetworkinfo { "version": 240001, "subversion": "/Satoshi:24.0.1/", "protocolversion": 70016, "localservices": "0000000000000409", "localservicesnames": [ "NETWORK", "WITNESS", "NETWORK_LIMITED" ], "localrelay": true, "timeoffset": -1, "networkactive": true, "connections": 10, "connections_in": 0, "connections_out": 10, "networks": [ "...detailed information about all networks..." ], "relayfee": 0.00001000, "incrementalfee": 0.00001000, "localaddresses": [ ], "warnings": "" }ซึ่งข้อมูลต่าง ๆ จะถูกส่งคืนในรูปแบบ JavaScript Object Notation (JSON) ซึ่งเป็นรูปแบบที่สามารถ "อ่าน" ได้อย่างง่ายดายโดยทุกภาษาโปรแกรมมิ่ง และยังเป็นรูปแบบที่มนุษย์อ่านได้ง่ายอีกด้วย ในข้อมูลนี้เราเห็นหมายเลขเวอร์ชันสำหรับซอฟต์แวร์ Bitcoin Core และโปรโตคอลบิตคอยน์เราเห็นจำนวนการเชื่อมต่อในปัจจุบันและข้อมูลต่างๆ เกี่ยวกับเครือข่ายบิตคอยน์และการตั้งค่าที่เกี่ยวข้องกับโหนดนี้
TIP: จะใช้เวลาสักระยะ อาจมากกว่าหนึ่งวัน สำหรับ bitcoind ในการอัพเดทให้ทันกับบล็อกล่าสุดของบล็อกเชนปัจจุบัน ในขณะที่มันดาวน์โหลดบล็อกจากโหนดอื่นๆ และตรวจสอบความถูกต้องของทุกธุรกรรมในบล็อกเหล่านั้น—ซึ่งมีเกือบหนึ่งพันล้านธุรกรรม ณ เวลาที่เขียนนี้ คุณสามารถตรวจสอบความคืบหน้าโดยใช้ getblockchaininfo เพื่อดูจำนวนบล็อกที่ทราบ ตัวอย่างในส่วนที่เหลือของบทนี้สมมติว่าคุณอยู่อย่างน้อยที่บล็อก 775,072 เนื่องจากความปลอดภัยของธุรกรรมขึ้นอยู่กับจำ
มาสำรวจและถอดรหัสธุรกรรมของบิตคอยน์กันเถอะ!!
อย่างในบทที่สอง อลิซได้ซื้อสินค้าจากร้านของบ็อบและธุรกรรมของเธอถูกบันทึกลงในบล็อกเชนของบิตคอยน์ โดยเราสามารถใช้ API เพื่อดึงและตรวจสอบธุรกรรมนั้นได้โดยการใช้ txid เป็นพารามิเตอร์:
$ bitcoin-cli getrawtransaction 466200308696215bbc949d5141a49a4138ecdfdfaa2a8029c1f9bcecd1f96177 --ผลลัพธ์ของคำสั่ง 01000000000101eb3ae38f27191aa5f3850dc9cad00492b88b72404f9da13569 8679268041c54a0100000000ffffffff02204e0000000000002251203b41daba 4c9ace578369740f15e5ec880c28279ee7f51b07dca69c7061e07068f8240100 000000001600147752c165ea7be772b2c0acb7f4d6047ae6f4768e0141cf5efe 2d8ef13ed0af21d4f4cb82422d6252d70324f6f4576b727b7d918e521c00b51b e739df2f899c49dc267c0ad280aca6dab0d2fa2b42a45182fc83e81713010000 0000TIP: txid ไม่ใช่สิ่งที่สามารถเชื่อถือได้ขนาดนั้น เพราะการไม่มี txid ในบล๊อกเชนของบิตคอยน์นั้นไม่ได้หมายความว่าธุรกรรมไม่ได้ถูกประมวลผล โดยสิ่งนี้เรียกว่า "transaction malleability" (ความสามารถในการเปลี่ยนแปลงธุรกรรม) เพราะธุรกรรมสามารถถูกแก้ไขก่อนการยืนยันในบล็อก ซึ่งเปลี่ยน txid ของพวกมัน หลังจากธุรกรรมถูกรวมอยู่ในบล็อกแล้ว txid ของมันไม่สามารถเปลี่ยนแปลงได้อีก เว้นแต่จะมีการจัดระเบียบบล็อกเชนใหม่และบล็อกนั้นถูกลบออกจากบล็อกเชนที่ดีที่สุด โดยการจัดระเบียบใหม่เกิดขึ้นได้ยากหลังจากธุรกรรมได้รับการยืนยันหลายครั้งแล้ว
คำสั่ง getrawtransaction จะส่งคืนธุรกรรมที่เข้ารหัสในรูปแบบเลขฐานสิบหกและเพื่อถอดรหัสนั้น เราใช้คำสั่ง decoderawtransaction โดยส่งข้อมูลเลขฐานสิบหกเป็นพารามิเตอร์ คุณสามารถคัดลอกเลขฐานสิบหกที่ส่งคืนโดย getrawtransaction และวางเป็นพารามิเตอร์ให้กับ decoderawtransaction ได้:
$ bitcoin-cli decoderawtransaction 01000000000101eb3ae38f27191aa5f3850dc9cad00492b88b72404f9da135698679268041c54a0100000000ffffffff02204e0000000000002251203b41daba4c9ace578369740f15e5ec880c28279ee7f51b07dca69c7061e07068f8240100000000001600147752c165ea7be772b2c0acb7f4d6047ae6f4768e0141cf5efe2d8ef13ed0af21d4f4cb82422d6252d70324f6f4576b727b7d918e521c00b51be739df2f899c49dc267c0ad280aca6dab0d2fa2b42a45182fc83e817130100000000 --ผลลัพธ์ของคำสั่ง { "txid": "466200308696215bbc949d5141a49a4138ecdfdfaa2a8029c1f9bcecd1f96177", "hash": "f7cdbc7cf8b910d35cc69962e791138624e4eae7901010a6da4c02e7d238cdac", "version": 1, "size": 194, "vsize": 143, "weight": 569, "locktime": 0, "vin": [ { "txid": "4ac541802679866935a19d4f40728bb89204d0cac90d85f3a51a19...aeb", "vout": 1, "scriptSig": { "asm": "", "hex": "" }, "txinwitness": [ "cf5efe2d8ef13ed0af21d4f4cb82422d6252d70324f6f4576b727b7d918e5...301" ], "sequence": 4294967295 } ], "vout": [ { "value": 0.00020000, "n": 0, "scriptPubKey": { "asm": "1 3b41daba4c9ace578369740f15e5ec880c28279ee7f51b07dca...068", "desc": "rawtr(3b41daba4c9ace578369740f15e5ec880c28279ee7f51b...6ev", "hex": "51203b41daba4c9ace578369740f15e5ec880c28279ee7f51b07d...068", "address": "bc1p8dqa4wjvnt890qmfws83te0v3qxzsfu7ul63kp7u56w8q...5qn", "type": "witness_v1_taproot" } }, { "value": 0.00075000, "n": 1, "scriptPubKey": { "asm": "0 7752c165ea7be772b2c0acb7f4d6047ae6f4768e", "desc": "addr(bc1qwafvze0200nh9vkq4jmlf4sy0tn0ga5w0zpkpg)#qq404gts", "hex": "00147752c165ea7be772b2c0acb7f4d6047ae6f4768e", "address": "bc1qwafvze0200nh9vkq4jmlf4sy0tn0ga5w0zpkpg", "type": "witness_v0_keyhash" } } ] }การถอดรหัสธุรกรรมแสดงส่วนประกอบทั้งหมดของธุรกรรมนี้ รวมถึงอินพุตและเอาต์พุตของธุรกรรม ในกรณีนี้เราเห็นว่าธุรกรรมใช้อินพุตหนึ่งรายการและสร้างเอาต์พุตสองรายการ อินพุตของธุรกรรมนี้คือเอาต์พุตจากธุรกรรมที่ได้รับการยืนยันก่อนหน้านี้ (แสดงเป็น txid ของอินพุต) เอาต์พุตทั้งสองรายการสอดคล้องกับการชำระเงินให้บ็อบและเงินทอนกลับให้อลิซ
มาสำรวจบล็อกของบิตคอยน์กัน!!
การสำรวจบล็อกนั้นคล้ายกับการสำรวจธุรกรรม แต่อย่างไรก็ตามบล็อกสามารถอ้างอิงได้ทั้งโดยลำดับของบล็อกหรือโดยแฮชของบล็อก เราใช้คำสั่ง getblockhash ซึ่งรับลำดับของบล็อกเป็นพารามิเตอร์และส่งคืน แฮชของบล็อกนั้น:
$ bitcoin-cli getblockhash 123456 --ผลลัพธ์ของคำสั่ง 0000000000002917ed80650c6174aac8dfc46f5fe36480aaef682ff6cd83c3caตอนนี้เรารู้แฮชสำหรับบล็อกที่เราเลือกแล้ว เราสามารถดูบล็อกนั้นได้ เราใช้คำสั่ง getblock โดยมีแฮชของบล็อกเป็นพารามิเตอร์:$ bitcoin-cli getblockhash 0000000000002917ed80650c6174aac8dfc46f5fe36480aaef682ff6cd83c3ca --ผลลัพธ์ของคำสั่ง { "hash": "0000000000002917ed80650c6174aac8dfc46f5fe36480aaef682ff6cd83c3ca", "confirmations": 651742, "height": 123456, "version": 1, "versionHex": "00000001", "merkleroot": "0e60651a9934e8f0decd1c[...]48fca0cd1c84a21ddfde95033762d86c", "time": 1305200806, "mediantime": 1305197900, "nonce": 2436437219, "bits": "1a6a93b3", "difficulty": 157416.4018436489, "chainwork": "[...]00000000000000000000000000000000000000541788211ac227bc", "nTx": 13, "previousblockhash": "[...]60bc96a44724fd72daf9b92cf8ad00510b5224c6253ac40095", "nextblockhash": "[...]00129f5f02be247070bf7334d3753e4ddee502780c2acaecec6d66", "strippedsize": 4179, "size": 4179, "weight": 16716, "tx": [ "5b75086dafeede555fc8f9a810d8b10df57c46f9f176ccc3dd8d2fa20edd685b", "e3d0425ab346dd5b76f44c222a4bb5d16640a4247050ef82462ab17e229c83b4", "137d247eca8b99dee58e1e9232014183a5c5a9e338001a0109df32794cdcc92e", "5fd167f7b8c417e59106ef5acfe181b09d71b8353a61a55a2f01aa266af5412d", "60925f1948b71f429d514ead7ae7391e0edf965bf5a60331398dae24c6964774", "d4d5fc1529487527e9873256934dfb1e4cdcb39f4c0509577ca19bfad6c5d28f", "7b29d65e5018c56a33652085dbb13f2df39a1a9942bfe1f7e78e97919a6bdea2", "0b89e120efd0a4674c127a76ff5f7590ca304e6a064fbc51adffbd7ce3a3deef", "603f2044da9656084174cfb5812feaf510f862d3addcf70cacce3dc55dab446e", "9a4ed892b43a4df916a7a1213b78e83cd83f5695f635d535c94b2b65ffb144d3", "dda726e3dad9504dce5098dfab5064ecd4a7650bfe854bb2606da3152b60e427", "e46ea8b4d68719b65ead930f07f1f3804cb3701014f8e6d76c4bdbc390893b94", "864a102aeedf53dd9b2baab4eeb898c5083fde6141113e0606b664c41fe15e1f" ] }รายการ confirmations บอกเราถึง ความลึก ของบล็อกนี้—มีกี่บล็อกที่ถูกสร้างทับบนบล็อกนี้ ซึ่งบ่งบอกถึงความยากในการเปลี่ยนแปลงธุรกรรมใดๆ ในบล็อกนี้ ลำดับบอกเราว่ามีกี่บล็อกที่มาก่อนหน้าบล็อกนี้ เราเห็นเวอร์ชันของบล็อก เวลาที่มันถูกสร้าง (ตามข้อมูลของนักขุด) เวลาเฉลี่ยของ 11 บล็อกที่มาก่อนหน้าบล็อกนี้ (การวัดเวลาที่นักขุดปลอมแปลงได้ยากกว่า) และขนาดของบล็อกในการวัดสามแบบต่างกัน (ขนาดดั้งเดิมที่ถูกลบข้อมูลบางส่วนออก, ขนาดเต็ม, และขนาดในหน่วยน้ำหนัก) เรายังเห็นฟิลด์บางอย่างที่ใช้สำหรับความปลอดภัยและหลักฐานการทำงาน (merkle root, nonce, bits, difficulty, และ chainwork) เราจะตรวจสอบสิ่งเหล่านี้โดยละเอียดในส่วนของการขุดในบทที่ 12การใช้อินเตอร์เฟสโปรแกรมของ Bitcoin Core
bitcoin-cli มีประโยชน์มากสำหรับการใช้งาน API ของ Bitcoin Core และการทดสอบฟังก์ชันต่าง ๆ แต่จุดประสงค์หลักของ API คือการเข้าถึงฟังก์ชันด้วยโปรแกรม ในส่วนนี้เราจะสาธิตการเข้าถึง Bitcoin Core จากโปรแกรมอื่น
API ของ Bitcoin Core เป็นอินเตอร์เฟส JSON-RPC โดย JSON เป็นวิธีที่สะดวกมากในการนำเสนอข้อมูลที่ทั้งมนุษย์และโปรแกรมสามารถอ่านได้ง่าย RPC ย่อมาจาก remote procedure call ซึ่งหมายความว่าเรากำลังเรียกใช้กระบวนการ (ฟังก์ชัน) ที่อยู่ห่างไกล (บนโหนด Bitcoin Core) ผ่านโปรโตคอลเครือข่าย ในกรณีนี้ โปรโตคอลเครือข่ายคือ HTTP
เมื่อเราใช้คำสั่ง bitcoin-cli เพื่อขอความช่วยเหลือเกี่ยวกับคำสั่ง มันแสดงตัวอย่างการใช้ curl ซึ่งเป็นไคลเอนต์ HTTP ทางคอมมานด์ไลน์ที่ยืดหยุ่น เพื่อสร้างคำเรียก JSON-RPC เหล่านี้:
$ curl --user myusername --data-binary '{"jsonrpc": "1.0", "id":"curltest", "method": "getblockchaininfo", "params": [] }' -H 'content-type: text/plain;' http://127.0.0.1:8332/คำสั่งนี้แสดงว่า curl ส่งคำขอ HTTP ไปยัง localhost (127.0.0.1) เชื่อมต่อกับพอร์ต RPC เริ่มต้นของ Bitcoin (8332) และส่งคำขอ jsonrpc โดยใช้เมธอดเป็น getblockchaininfo โดยใช้การเข้ารหัสแบบ text/plain
คุณอาจสังเกตว่า curl จะขอให้ส่งข้อมูลประจำตัวไปพร้อมกับคำขอ Bitcoin Core จะสร้างรหัสผ่านแบบสุ่มในแต่ละครั้งที่เริ่มต้นและวางไว้ในไดเรกทอรีข้อมูลภายใต้ชื่อ .cookie โดย bitcoin-cli สามารถอ่านไฟล์รหัสผ่านนี้โดยให้ไดเรกทอรีข้อมูล ในทำนองเดียวกัน คุณสามารถคัดลอกรหัสผ่านและส่งไปยัง curl (หรือตัวครอบ Bitcoin Core RPC ระดับสูงอื่น ๆ ) ตามที่เห็นในการใช้การตรวจสอบสิทธิ์แบบใช้คุกกี้กับ Bitcoin Core
ตัวอย่างที่ 3. การใช้การตรวจสอบสิทธิ์แบบใช้คุกกี้กับ Bitcoin Core
$ cat .bitcoin/.cookie __cookie__:17c9b71cef21b893e1a019f4bc071950c7942f49796ed061b274031b17b19cd0 $ curl --user __cookie__:17c9b71cef21b893e1a019f4bc071950c7942f49796ed061b274031b17b19cd0 --data-binary '{"jsonrpc": "1.0", "id":"curltest", "method": "getblockchaininfo", "params": [] }' -H 'content-type: text/plain;' http://127.0.0.1:8332/ {"result":{"chain":"main","blocks":799278,"headers":799278, "bestblockhash":"000000000000000000018387c50988ec705a95d6f765b206b6629971e6978879", "difficulty":53911173001054.59,"time":1689703111,"mediantime":1689701260, "verificationprogress":0.9999979206082515,"initialblockdownload":false, "chainwork":"00000000000000000000000000000000000000004f3e111bf32bcb47f9dfad5b", "size_on_disk":563894577967,"pruned":false,"warnings":""},"error":null, "id":"curltest"}นอกจากนี้คุณยังสามารถตั้งรหัสผ่านด้วยตัวเองใน ./share/rpcauth/rpcauth.py ภายในไดเรกทอรีของ Bitcoin Core
หากคุณกำลังใช้การเรียก JSON-RPC ในโปรแกรมของคุณเอง คุณสามารถใช้ไลบรารี HTTP ทั่วไปเพื่อสร้างการเรียกได้ คล้ายกับที่แสดงในตัวอย่าง curl ก่อนหน้านี้
อย่างไรก็ตาม มีไลบรารีในภาษาโปรแกรมยอดนิยมส่วนใหญ่ที่ "wrap" API ของ Bitcoin Core ในลักษณะที่ทำให้การใช้งานง่ายขึ้นมาก เราจะใช้ไลบรารี python-bitcoinlib เพื่อทำให้การเข้าถึง API นั้นง่ายขึ้น โดยไลบรารีนี้ไม่ได้เป็นส่วนหนึ่งของโครงการ Bitcoin Core และจำเป็นต้องติดตั้งด้วยวิธีปกติที่คุณติดตั้งไลบรารี Python โปรดจำไว้ว่า การใช้งานนี้ต้องมีอินสแตนซ์ Bitcoin Core ที่กำลังทำงานอยู่ ซึ่งจะถูกใช้เพื่อทำการเรียก JSON-RPC
ตัวอย่างสคริปต์ Python ใน " การทำงาน getblockchaininfo ผ่าน API JSON-RPC ของ Bitcoin Core" ซึ่งทำการเรียก getblockchaininfo อย่างง่ายและพิมพ์พารามิเตอร์ block จากข้อมูลที่ส่งคืนโดย Bitcoin Core
ตัวอย่างที่ 4. การทำงาน getblockchaininfo ผ่าน API JSON-RPC ของ Bitcoin Core ``` from bitcoin.rpc import RawProxy
Create a connection to local Bitcoin Core node
p = RawProxy()
Run the getblockchaininfo command, store the resulting data in info
info = p.getblockchaininfo()
Retrieve the 'blocks' element from the info
print(info['blocks']) --ผลลัพธ์ของคำสั่ง $ python rpc_example.py 773973 ``` มันบอกเราว่าโหนด Bitcoin Core ในเครื่องของเรามีกี่บล็อกในบล็อกเชนของมัน ซึ่งไม่ใช่ผลลัพธ์ที่น่าทึ่ง แต่มันแสดงการใช้งานพื้นฐานของไลบรารีในฐานะอินเตอร์เฟสที่ถูกทำให้ง่ายขึ้นสำหรับ API JSON-RPC ของ Bitcoin Core
ต่อไป เราจะใช้คำสั่ง getrawtransaction และ decodetransaction เพื่อดึงข้อมูลรายละเอียดของการชำระเงินจาก Alice ไปยัง Bob ในส่วนของการดึงข้อมูลธุรกรรมและการวนลูปเอาต์พุตของธุรกรรม เราจะดึงธุรกรรมของ Alice และแสดงรายการเอาต์พุตของธุรกรรม สำหรับแต่ละเอาต์พุต เราจะแสดงที่อยู่ผู้รับและมูลค่า โดยธุรกรรมของ Alice มีเอาต์พุตหนึ่งรายการที่จ่ายให้ Bob และอีกหนึ่งรายการเป็นเงินทอนกลับไปยัง Alice
ตัวอย่างที่ 5 การดึงข้อมูลธุรกรรมและการวนลูปเอาต์พุตของธุรกรรม ``` from bitcoin.rpc import RawProxy p = RawProxy()
Alice's transaction ID
txid = "466200308696215bbc949d5141a49a4138ecdfdfaa2a8029c1f9bcecd1f96177"
First, retrieve the raw transaction in hex
raw_tx = p.getrawtransaction(txid)
Decode the transaction hex into a JSON object
decoded_tx = p.decoderawtransaction(raw_tx)
Retrieve each of the outputs from the transaction
for output in decoded_tx['vout']: print(output['scriptPubKey']['address'], output['value']) --ผลลัพธ์ของคำสั่ง $ python rpc_transaction.py bc1p8dqa4wjvnt890qmfws83te0v3qxzsfu7ul63kp7u56w8qc0qwp5qv995qn 0.00020000 bc1qwafvze0200nh9vkq4jmlf4sy0tn0ga5w0zpkpg 0.00075000 ``` ตัวอย่างทั้งสองข้างต้นค่อนข้างง่าย คุณไม่จำเป็นต้องใช้โปรแกรมในการรันพวกมัน คุณสามารถใช้ตัวช่วย bitcoin-cli ได้ง่าย ๆ แต่อย่างไรก็ตาม ตัวอย่างถัดไปต้องใช้การเรียก RPC หลายร้อยครั้งและแสดงให้เห็นถึงการใช้อินเทอร์เฟซเชิงโปรแกรมได้ชัดเจนยิ่งขึ้น
ในส่วนของการดึงข้อมูลบล็อกและการรวมเอาต์พุตของทุกธุรกรรม เราจะเริ่มต้นด้วยการดึงข้อมูลบล็อก จากนั้นดึงข้อมูลธุรกรรมแต่ละรายการภายในบล็อกโดยอ้างอิงถึง ID ของแต่ละธุรกรรม ต่อมา เราจะวนลูปผ่านเอาต์พุตของแต่ละธุรกรรมและรวมมูลค่าทั้งหมด
ตัวอย่างที่ 6 การดึงข้อมูลบล็อกและการรวมเอาต์พุตของทุกธุรกรรม ``` from bitcoin.rpc import RawProxy p = RawProxy()
The block height where Alice's transaction was recorded
blockheight = 775072
Get the block hash of the block at the given height
blockhash = p.getblockhash(blockheight)
Retrieve the block by its hash
block = p.getblock(blockhash)
Element tx contains the list of all transaction IDs in the block
transactions = block['tx'] block_value = 0
Iterate through each transaction ID in the block
for txid in transactions: tx_value = 0 # Retrieve the raw transaction by ID raw_tx = p.getrawtransaction(txid) # Decode the transaction decoded_tx = p.decoderawtransaction(raw_tx) # Iterate through each output in the transaction for output in decoded_tx['vout']: # Add up the value of each output tx_value = tx_value + output['value'] # Add the value of this transaction to the total block_value = block_value + tx_value print("Total value in block: ", block_value) --ผลลัพธ์ของคำสั่ง $ python rpc_block.py Total value in block: 10322.07722534 ```
โค้ดตัวอย่างของเราคำนวณว่ามูลค่ารวมที่ถูกทำธุรกรรมในบล็อกนี้คือ 10,322.07722534 BTC (รวมถึงรางวัล 25 BTC และค่าธรรมเนียม 0.0909 BTC) ลองเปรียบเทียบกับจำนวนที่รายงานโดยเว็บไซต์สำรวจบล็อก (block explorer) โดยการค้นหาแฮชของบล็อกหรือเลขลำดับของบล็อก เครื่องมือสำรวจบล็อกบางตัวรายงานมูลค่ารวมโดยไม่รวมรางวัลและไม่รวมค่าธรรมเนียม ลองดูว่าคุณสามารถสังเกตเห็นความแตกต่างได้หรือไม่
ไคลเอนต์ทางเลือก, ไลบรารี, และชุดเครื่องมือ
C/C++ Bitcoin Core:การใช้งานอ้างอิงของ Bitcoin JavaScript bcoin: การใช้งานโหนดแบบเต็มรูปแบบที่มีความยืดหยุ่นและขยายได้พร้อม API Bitcore: โหนดเต็มรูปแบบ, API, และไลบรารีโดย Bitpay BitcoinJS: ไลบรารี Bitcoin ที่เขียนด้วย JavaScript ล้วนๆ สำหรับ node.js และเบราว์เซอร์ Java bitcoinj: ไลบรารีไคลเอนต์โหนดเต็มรูปแบบที่เขียนด้วย Java Python python-bitcoinlib: ไลบรารี Bitcoin, ไลบรารีฉันทามติ, และโหนดที่เขียนด้วย Python โดย Peter Todd pycoin: ไลบรารี Bitcoin ที่เขียนด้วย Python โดย Richard Kiss Go btcd: ไคลเอนต์ Bitcoin โหนดเต็มรูปแบบที่เขียนด้วยภาษา Go Rust rust-bitcoin: ไลบรารี Bitcoin ที่เขียนด้วย Rust สำหรับการจัดรูปแบบข้อมูล, การแยกวิเคราะห์, และการเรียกใช้ API Scala bitcoin-s: การใช้งาน Bitcoin ที่เขียนด้วย Scala C# NBitcoin: ไลบรารี Bitcoin ที่ครอบคลุมสำหรับเฟรมเวิร์ก .NET
ยังมีไลบรารีอีกมากมายในภาษาโปรแกรมมิ่งอื่น ๆ อีกหลากหลาย และมีการสร้างขึ้นใหม่อยู่ตลอดเวลา
หากคุณทำตามคำแนะนำในบทนี้ ตอนนี้คุณมี Bitcoin Core ที่ทำงานอยู่และได้เริ่มสำรวจเครือข่ายและบล็อกเชนโดยใช้โหนดของคุณเอง จากนี้ไปคุณสามารถใช้ซอฟต์แวร์ที่คุณควบคุมได้โดยอิสระ—บนคอมพิวเตอร์ที่คุณควบคุม—เพื่อตรวจสอบว่า bitcoin ใด ๆ ที่คุณได้รับปฏิบัติตามกฎทุกข้อในระบบ Bitcoin โดยไม่ต้องไว้วางใจองค์กรภายนอกใด ๆ ในบทต่อไป เราจะเรียนรู้เพิ่มเติมเกี่ยวกับกฎของระบบและวิธีที่โหนดและกระเป๋าเงินของคุณใช้กฎเหล่านั้นเพื่อรักษาความปลอดภัยของเงินของคุณ ปกป้องความเป็นส่วนตัวของคุณ และทำให้การใช้จ่ายและการรับเงินสะดวกสบาย
ฮึ่ ๆ หลาม ๆ มาอีกแล้ว จริง ๆ เนื้อหาของบทที่สามมันจบลงตรงนี้แหละ แต่ว่าถ้าสมมุตืว่าใครลองไปทำตามจริง ๆ แล้วอยากรู้ว่าเราสามารถทำอะไรจาก node ของเราได้อีกบ้าง เลยมีกิจกรรมขำ ๆ มาให้ทำครับ โดยความยากจะมีทั้งหมด 3 ระดับ ดังนี้
- ง่าย (สามารถหาคำตอบได้ด้วย bitcoin-cli command เดียว)
- แฮชของบล๊อก 774698 คืออะไร?
-
signature ของข้อความจาก address นี้ถูกต้องหรือไม่
address: 1E9YwDtYf9R29ekNAfbV7MvB4LNv7v3fGa message: 1E9YwDtYf9R29ekNAfbV7MvB4LNv7v3fGa signature:HCsBcgB+Wcm8kOGMH8IpNeg0H4gjCrlqwDf/GlSXphZGBYxm0QkKEPhh9DTJRp2IDNUhVr0FhP9qCqo2W0recNM= -
ทำได้แหละ (สามารถหาคำตอบได้ด้วย bitcoin-cli command เดียว หรืออาจจะมากกว่าหนึ่ง)
- มี output ใหม่กี่อันที่เกิดในบล๊อก 774698 ?
- ใช้ wallet descriptors หา taproot address ที่ 100 จาก extended public key ที่กำหนดให้ xpub6DLd5RvY42Q5HAmBhHPUbDGdeS9VvsYNauiuN8r6NzbiXSSNWpNVrDGTUScJ9fS2orMtuB3VdxMdUH83fPtwbrizfJg9LwWnGqtL7RTs5h1
-
สร้าง multisig address แบบ P2SH แบบ 1-of-4 จาก publickey ในอินพุตทั้งสี่ของธุรกรรมนี้:37d966a263350fe747f1c606b159987545844a493dd38d84b070027a895c4517
-
ต้องคิดเชิงตรรกะได้เล็กน้อย (สามารถหาคำตอบได้ด้วย bitcoin-cli command และพวก if-else/loop)
- tx ใดในบล็อก 257,343 ที่ใช้เอาท์พุตของ coinbase ของบล็อก 256,128?
- มีเอาต์พุตเดียวที่ยังไม่ได้ใช้งานจากบล็อก 123,321 เอาต์พุตดังกล่าวถูกส่งไปที่ address ไหน
- public key ใดที่ลงนามอินพุต 0 ใน tx นี้:e5969add849689854ac7f28e45628b89f7454b83e9699e551ce14b6f90c86163
ใครทำได้พร้อมแชร์วิธีการใต้โพสต์นี้เดี๋ยวจะมีไดโนเสาร์ส่งแซตเป็นกำลังใจให้เล็กน้อยครับ
-
 @ da0b9bc3:4e30a4a9
2025-03-08 07:03:33
@ da0b9bc3:4e30a4a9
2025-03-08 07:03:33Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/907271
-
 @ 220522c2:61e18cb4
2025-03-08 06:19:30
@ 220522c2:61e18cb4
2025-03-08 06:19:30Comet is available on Linux

The Comet longform desktop app is available as an AppImage for Linux.
linux
-
 @ 291c75d9:37f1bfbe
2025-03-08 04:09:59
@ 291c75d9:37f1bfbe
2025-03-08 04:09:59In 1727, a 21-year-old Benjamin Franklin gathered a dozen men in Philadelphia for a bold experiment in intellectual and civic growth. Every Friday night, this group—known as the Junto, from the Spanish juntar ("to join")—met in a tavern or private home to discuss "Morals, Politics, or Natural Philosophy (science)." Far from a casual social club, the Junto was a secret society dedicated to mutual improvement, respectful discourse, and community betterment. What began as a small gathering of tradesmen and thinkers would leave a lasting mark on Franklin’s life and colonial America.
Printers are educated in the belief that when men differ in opinion, both sides ought equally to have the advantage of being heard by the public, and that when Truth and Error have fair play, the former is always an overmatch for the latter. - Benjamin Franklin
The Junto operated under a clear set of rules, detailed by Franklin in his Autobiography:
"The rules that I drew up required that every member, in his turn, should produce one or more queries on any point of Morals, Politics, or Natural Philosophy, to be discuss’d by the company; and once in three months produce and read an essay of his own writing, on any subject he pleased. Our debates were to be under the direction of a president, and to be conducted in the sincere spirit of inquiry after truth, without fondness for dispute, or desire of victory; and, to prevent warmth [heatedness], all expressions of positiveness in opinions, or direct contradiction, were after some time made contraband and prohibited under small pecuniary penalties [monetary fines]."
These guidelines emphasized collaboration over competition. Members were expected to contribute questions or essays, sparking discussions that prioritized truth over ego. To keep debates civil, the group even imposed small fines for overly assertive or contradictory behavior—a practical nudge toward humility and open-mindedness. (Yes, I believe that is an ass tax!)
Rather than admitting new members, Franklin encouraged existing ones to form their own discussion groups. This created a decentralized network of groups ("private relays," as I think of them), echoing the structure of modern platforms like NOSTR—while preserving the Junto’s exclusivity and privacy.
From the beginning, they made it a rule to keep these meetings secret, without applications or admittance of new members. Instead, Franklin encouraged members to form their own groups—in a way acting as private relays of sorts. (I say "private" because they continued to keep the Junto secret, even with these new groups.)
Membership: A Diverse Circle United by Values
The Junto’s twelve founding members came from varied walks of life—printers, surveyors, shoemakers, and clerks—yet shared a commitment to self-improvement. Franklin, though the youngest (around 21 when the group formed), led the Junto with a vision of collective growth. To join, candidates faced a simple vetting process, answering four key questions:
- Have you any particular disrespect for any present members? Answer: I have not.
- Do you sincerely declare that you love mankind in general, of what profession or religion soever? Answer: I do.
- Do you think any person ought to be harmed in his body, name, or goods, for mere speculative opinions, or his external way of worship? Answer: No.
- Do you love truth for truth’s sake, and will you endeavor impartially to find and receive it yourself and communicate it to others? Answer: Yes.
These criteria reveal the Junto’s core values: respect, tolerance, and an unwavering pursuit of truth. They ensured that members brought not just intellect but also character to the table—placing dialogue as the priority.
One should also note the inspiration from the "Dry Club" of John Locke, William Popple, and Benjamin Furly in the 1690s. They too required affirmation to:
- Whether he loves all men, of what profession or religion soever?
- Whether he thinks no person ought to be harmed in his body, name, or goods, for mere speculative opinions, or his external way of worship?
- Whether he loves and seeks truth for truth’s sake; and will endeavor impartially to find and receive it himself, and to communicate it to others?
And they agreed: "That no person or opinion be unhandsomely reflected on; but every member behave himself with all the temper, judgment, modesty, and discretion he is master of."
The Discussions: 24 Questions to Spark Insight
Franklin crafted a list of 24 questions to guide the Junto’s conversations, ranging from personal anecdotes to civic concerns. These prompts showcase the group’s intellectual breadth. Here are some of my favorites:
Hath any citizen in your knowledge failed in his business lately, and what have you heard of the cause? Have you lately heard of any citizen’s thriving well, and by what means? Do you know of any fellow citizen who has lately done a worthy action, deserving praise and imitation? Do you think of anything at present in which the Junto may be serviceable to mankind, their country, friends, or themselves? Have you lately observed any defect in the laws of your country, which it would be proper to move the legislature for an amendment? Do you know of any deserving young beginner lately set up, whom it lies in the power of the Junto any way to encourage?
(Read them all here.)
Note the keen attention to success and failure, and the reflection on both. Attention was often placed on the community and individual improvement beyond the members of the group. These questions encouraged members to share knowledge, reflect on virtues and vices, and propose solutions to real-world problems. The result? Discussions that didn’t just end at the tavern door but inspired tangible community improvements.
The Junto’s Legacy: America’s First Lending Library
One of the Junto’s most enduring contributions to Philadelphia—and indeed, to the American colonies—was the creation of the first lending library in 1731. Born from the group’s commitment to mutual improvement and knowledge-sharing, this library became a cornerstone of public education and intellectual life in the community.
The idea for the library emerged naturally from the Junto’s discussions. Members, who came from diverse backgrounds but shared a passion for learning, recognized that their own access to books was often limited and costly—and they referred to them often. To address this, they proposed pooling their personal collections to create a shared resource. This collaborative effort allowed them—and eventually the broader public—to access a wider range of books than any individual could afford alone.
The library operated on a simple yet revolutionary principle: knowledge should be available to all, regardless of wealth or status. By creating a lending system, the Junto democratized access to information, fostering a culture of self-education and curiosity. This was especially significant at a time when books were scarce and formal education was not universally accessible.
The success of the Junto’s library inspired similar initiatives across the colonies, laying the groundwork for the public library system we know today. It also reflected the group’s broader mission: to serve not just its members but the entire community. The library became a symbol of the Junto’s belief in the power of education to uplift individuals and society alike.
With roots extending back to the founding of the Society in 1743, the Library of the American Philosophical Society houses over thirteen million manuscripts, 350,000 volumes and bound periodicals, 250,000 images, and thousands of hours of audiotape. The Library’s holdings make it one of the premier institutions for documenting the history of the American Revolution and Founding, the study of natural history in the 18th and 19th centuries, the study of evolution and genetics, quantum mechanics, and the development of cultural anthropology, among others.
The American Philosophical Society Library continues today. I hope to visit it myself in the future.
Freedom, for Community
Comparing the Junto to Nostr shows how the tools of community and debate evolve with time. Both prove that people crave spaces to connect, share, and grow—whether in a colonial tavern or a digital relay. Yet their differences reveal trade-offs: the Junto’s structure offered depth and focus but capped its reach, while Nostr’s openness promises scale at the cost of order.
In a sense, Nostr feels like the Junto’s modern echo—faster, bigger, and unbound by gates or rules. Franklin might admire its ambition, even if he’d raise an eyebrow at its messiness. For us, the comparison underscores a timeless truth: no matter the medium, the drive to seek truth and build community endures.
The Autobiography of Benjamin Franklin (1771–1790, pub. 1791)
http://www.benjamin-franklin-history.org/junto-club/
Benjamin Franklin, Political, Miscellaneous, and Philosophical Pieces, ed. Benjamin Vaughan (London: 1779), pp. 533–536.
"Rules of a Society" in The Remains of John Locke, Esq. (1714), p. 113
npubpro
-
 @ 220522c2:61e18cb4
2025-03-08 03:51:09
@ 220522c2:61e18cb4
2025-03-08 03:51:09Enable trackpad pinch zoom for Brave on Linux
-
Open Brave: Launch the Brave browser.
-
Access Flags: Type brave://flags in the address bar and press Enter.
-
Search for Ozone Platform:In the search bar at the top, type ozone.
-
Find
Preferred Ozone platform -
Set it to
Wayland -
Done
-
-
 @ c3ae4ad8:e54d46cb
2025-03-08 03:38:15
@ c3ae4ad8:e54d46cb
2025-03-08 03:38:15This is for one serving (I'm currently doing a >500 cal low carb meal plan). Next time, I'll scramble an egg in there to up the protein a little more. High-protein, low-carb stir fry made with turkey, broccoli, snow peas, green onions, savoy cabbage, bok choy, garlic, in a sesame, soy and ginger sauce.
INGREDIENTS
- 1/3 lb / 170g ground turkey (I used 93% lean, hormone-free/organic)
- 2 tsp light olive oil or coconut oil
- 3 TB soy sauce, tamari, or coconut aminos
- 1 cup / 85g mixed stir fry greens, your choice (cabbage, bok choy, etc.)
- Half a bunch of green onion, roughly chopped, green parts only
- Dash of crushed red pepper flakes
- 1 clove minced garlic
- 1 tsp minced ginger
- Sesame seeds (optional, black, regular, or both!)
- 1 tsp sesame oil
DIRECTIONS
1. Heat oil in a skillet and add the ground turkey once the oil starts to shimmer.
2. On medium-high heat, cook the ground turkey, breaking it into bite-size pieces as it cooks, drizzling 1 TB of the soy sauce over the meat a little at a time. You want to evaporate the water out of the meat, so keep letting it cook until it's actually browned—the soy sauce helps with this, but you want the milliard reaction here (look it up and thank me later)!
3. Decrease the heat to low. Push the cooked turkey to one side and tilt the pan a bit away from you so the oil is isolated, and add the garlic into the oil and stir it in there a little bit.
4. Once the garlic is fragrant, stir the meat back into the garlic, toss in the chopped veggies, green onions, and remaining 1 TB of soy sauce. Then add the minced ginger and red pepper flakes on top, and quickly cover the pan with a lid. Let it steam for about 6-8 minutes on medium-low heat.
5. After the veggies are cooked, stir the little pile of steamed ginger into the mix, drizzle the sesame seed oil over the meat and veggies, stir again, and serve hot with optional sesame seeds as a garnish. Enjoy!
For more food and recipes by me, visit https://ketobeejay.npub.pro/ and click on "recipes" at the top
-
 @ 7b3f7803:8912e968
2025-03-08 03:05:16
@ 7b3f7803:8912e968
2025-03-08 03:05:16Libertarians believe in open borders in theory. In practice, open borders don't work, because, among other things, the combination with a welfare state creates a moral hazard, and the least productive of society end up within the borders of welfare states and drain resources. The social services are paid by the productive people of the country or, in the case of most fiat systems, by currency holders through inflation. Welfare states are much more likely under fiat money and the redistribution goes from native taxpayers to illegal immigrants. Thus, under fiat money, open borders end up being an open wound by which the productive lifeblood of the country bleeds out, despite the theoretical trade-efficiency benefits. As libertarians like to say, open borders and the welfare state don't mix. In this article, we'll examine the other sacred cow of libertarian thought: free trade.
Free Trade without Libertarian Ideals
Free trade is very similar to free movement of labor in that it works great in theory, but not in practice, especially under fiat money. In a libertarian free-market world, free trade works. But that assumes a whole host of libertarian ideals like sound money, non-interfering governments, and minimal aggression. Once those ideals are violated, such as with government intervention in the market, similar moral hazards and long-term costs come with them, making free trade about as libertarian as a fractional reserve bank.
An example will illustrate what I'm talking about. Let's say Portugal subsidizes their wine for export to other countries. The obvious first-order effect is that it makes Portuguese wine cheaper in France, perhaps undercutting the price of French wine. Libertarians would say, that's great! French customers get cheaper goods, so what's the problem?
As with any government intervention, there are significant second- and third-order effects in play. Subsidization puts unsubsidized companies at risk, perhaps driving them to bankruptcy. In this case, this might be a French wine maker. Subsidized companies may become zombies instead of dying out. In this case, this might be a Portuguese wine maker that was failing domestically but survives by selling to customers abroad with government subsidies. While French customers benefit in the short run with cheaper prices for wine, they are ultimately hurt because the goods that would have existed without government intervention never come to market. Perhaps French wine makers that went bankrupt were innovating. Perhaps the resources of the zombie Portuguese wine maker would have created something better.
Further, the dependency of French people on Portuguese wine means that something going wrong in Portugal, like a war or subsidy cuts, disrupts the supply and price of wine for France. Now France must meddle in Portugal internationally if it doesn't want the wine supply to get disrupted. The two countries get entangled in such a way as to become more interventionist internationally. A war involving Portugal now suddenly becomes France's business and incentivizes military aid or even violence. As usual, the unseen effects of government policy are the most pernicious.
Not Really Free
In other words, what we call free trade isn't really free trade. A country exporting to the US may subsidize their products through government intervention, making the product cheaper in the US. This hurts US companies, and they’re forced into choices they never would have had to face without the foreign government intervention. But because the good is crossing borders under the rubric of "free trade," it's somehow seen as fair. Of course it's not, as government intervention distorts the market whether it's done by our own government or a foreign government.
So why would a foreign government do this? It gets several benefits through targeted market manipulation. First, it makes its own companies' products more popular abroad and conversely, makes US companies' products less popular. This has the dual benefit of growing the foreign government’s firms and shrinking, perhaps bankrupting, the US ones.
Targeted subsidization like this can lead to domination under free trade. It's not unlike the Amazon strategy of undercutting everyone first and using the monopoly pricing power at scale once everyone else has bankrupted. The global monopoly is tremendously beneficial to the country that has it. Not only is there significant tax revenue over the long term, but also a head start on innovations within that industry and an advantage in production in the adjacent industries around the product.
Second, the manufacturing centralization gives that country leverage geo-politically. A critical product that no one else manufactures means natural alliances with the countries that depend on the product, which is especially useful for smaller countries like Taiwan. Their chip manufacturing industry, holding 60% of global supply (2024), has meant that they're a critical link for most other countries, and hence, they can use this fact to deter Chinese invasion.
Third, because of the centralization of expertise, more innovations, products, and manufacturing will tend to come within the country. This increased production has cascading benefits, including new industries and national security. China leads the world in drone technology, which undoubtedly has given it an innovation advantage for its military, should it go to war.
Fourth, the capital that flows into the country for investing in the monopolized industry will tend to stay, giving the country more wealth in the form of factories, equipment, and skills. While that capital may nominally be in the hands of foreigners, over time, the ownership of that industry will inevitably transition toward native locals, as the knowledge about how to run such industries gets dissipated within the country.
[Image: Map showing “China Drone Tech” and “Taiwan Chips” hubs, with arrows of capital flow staying local]
Currency Devaluation: The Universal Trade Weapon
It would be one thing if only a specific industry were singled out for government subsidies and then the products dumped into the US as a way to hurt US companies, as that would limit the scope of the damage. But with currency devaluation, a government can subsidize all of its exports at the same time. Indeed, this is something that many countries do. While short-term, this helps US consumers, it hurts US companies and forces them into decisions that aren't good for the US.
To compete, they have to lower costs by using the same devalued currency to pay their labor as their foreign competition. That is, by relocating their capital, their manufacturing, and even their personnel to the country that's devaluing the currency. Not only does relocating reduce labor cost, but it also often gets them benefits like tax breaks. This makes US companies de facto multinationals and not only makes them subject to other jurisdictions, but ultimately divides their loyalties. To take advantage of the reduced labor, capital must move to another country and, along with it, future innovation.
Such relocations ultimately leave the company stripped of their manufacturing capability in the US, as local competition will generally fare better over the long run. Much of the value of the industry then is captured by other governments in taxes, development, and even state-owned companies. Free trade, in other words, creates a vulnerability for domestic companies as they can be put at a significant disadvantage compared to foreign counterparts.
Hidden Effects of Foreign Intervention
Unlike the multinationals, small companies have no chance as they're not big enough to exploit the labor arbitrage. And as is usual in a fiat system, they suffer the most while the giant corporations get the benefits of the supposed "free trade". Most small companies can't compete, so we get mostly the bigger companies that survive.
The transition away from domestic manufacturing necessarily means significant disruption. Domestic workers are displaced and have to find new work. Factories and equipment either have to be repurposed or rot. Entire communities that depended on the manufacturing facility now have to figure out new ways to support themselves. It's no good telling them that they can just do something else. In a currency devaluation scenario, most of the manufacturing leaves and the jobs left are service-oriented or otherwise location-based, like real estate development. There's a natural limit to location-based industries because the market only grows with the location that you're servicing. Put another way, you can only have so many people give haircuts or deliver packages in a geographic area. There has to be some manufacturing of goods that can be sold outside the community, or the community will face scarce labor opportunities relative to the population.
You also can't say the displaced workers can start some other manufacturing business. Such businesses will get out-competed on labor by the currency-devaluing country, so there won't be much investment available for such a business, and even if there were, such a business would be competing with its hands tied behind its back. So in this scenario, what you end up with are a large pool of unemployed people whom the state subsidizes with welfare.
So when a US company leaves or goes bankrupt due to a foreign government's subsidies, the disruption alone imposes a significant short-term cost with displaced labor, unused capital goods, and devastated communities.
Mitigations
So how do countries fight back against such a devastating economic weapon? There are a few ways countries have found around this problem of currency devaluation under free trade. First, a country can prevent capital from leaving. This is called capital controls, and many countries, particularly those that manufacture a lot, have them. Try to get money, factories, or equipment out of Malaysia, for example, and you'll find that they make it quite difficult. Getting the same capital into the country, on the other hand, faces few restrictions. Unfortunately, the US can't put in capital controls because dollars are its main export. It is, after all, the reserve currency of the world.
Second, you can compete by devaluing your own currency. But that’s very difficult because it requires printing a lot of dollars, and that causes inflation. There's also no guarantee that a competing country doesn't devalue its currency again. The US is also in a precarious position as the world's reserve currency, so devaluing the currency more than it already does will make other holders of the dollar less likely to want to hold it, threatening the reserve currency status.
So the main two mitigations against currency devaluation in a free trade scenario are not available to the US. So what else is there? The remaining option is to drop free trade. The solution, in other words, is to add tariffs. This is how you can nullify the effects of foreign government intervention, by leveling the playing field for US manufacturers.
Tariffs
One major industry that's managed to continue being manufactured in the US despite significant foreign competition is cars. Notably, cars have a tariff, which incentivizes their manufacture in the US, even for foreign car makers. The tariff has acted as a way to offset foreign government subsidies and currency debasement.
The scope of this one industry for the US is huge. There are around 300,000 direct jobs in auto assembly within the US (USTR) and there are an additional 3 million jobs supplying these manufacturers within the US. But the benefits don't end there. The US is also creating a lot of innovation around cars, such as self-driving and plug-in electric cars. There are many countries that would love to have this industry for themselves, but because of tariffs, auto manufacturing continues in the US.
And though tariffs are seen as a tax on consumers, US car prices are cheap relative to the rest of the world. What surprises a lot of people when they move from the US to other countries is finding out that the same car often costs more abroad (e.g. 25% tariffs keep U.S. prices 20% below Europe’s $40K average, 2024). The downside of tariffs pales next to the downsides of "free trade."
Free Trade Doesn’t Work with Fiat Money
The sad reality is that while we would love for free trade to work in the ideal libertarian paradise, it won't in our current fiat-based system. The subsidization by foreign governments to bankrupt US companies or to make them multinational, combined with the unfortunate reality of the US dollar being the world reserve currency, means that free trade guts the US of manufacturing. Tariffs are a reasonable way to protect US manufacturers, particularly smaller ones that can't go multinational.
What's more, tariffs make the US less fragile and less dependent on international supply chains. Many of the wars in the past 60 years have been waged because of the entanglements the US has with other countries due to the reliance on international supply chains. Lessening this dependency, if only to prevent a war, has clear value.
Lastly, labor has been devalued significantly by fiat monetary expansion, but at least some of that can be recovered if tariffs create more manufacturing, which in turn adds to the demand for labor. This should reduce the welfare state as more opportunities are made available and fewer unemployed people will be on the rolls.
Conclusion
Fiat money produces a welfare state, which makes open borders unworkable. Fiat money also gives foreign governments a potent economic weapon to use against US companies, and by extension the labor force that powers them. Though currency debasement and capital controls are available to other countries as a defense, for the US, neither of these tools is available due to the fact that the dollar is the world reserve currency. As such, tariffs are a reasonable defense against the fiat subsidization of foreign governments.
-
 @ 7b3f7803:8912e968
2025-03-08 02:28:40
@ 7b3f7803:8912e968
2025-03-08 02:28:40 Libertarians believe in open borders in theory. In practice, open borders don’t work, because, among other things, the combination with a welfare state creates a moral hazard, and the least productive of society end up within the borders of welfare states and drain resources. The social services are paid by the productive people of the country or, in the case of most fiat systems, by currency holders through inflation. Welfare states are much more likely under fiat money and the redistribution goes from native taxpayers to illegal immigrants. Thus, under fiat money, open borders end up being an open wound by which the productive lifeblood of the country bleeds out, despite the theoretical trade-efficiency benefits. As libertarians like to say, open borders and the welfare state don’t mix. In this article, we’ll examine the other sacred cow of libertarian thought: free trade.
Libertarians believe in open borders in theory. In practice, open borders don’t work, because, among other things, the combination with a welfare state creates a moral hazard, and the least productive of society end up within the borders of welfare states and drain resources. The social services are paid by the productive people of the country or, in the case of most fiat systems, by currency holders through inflation. Welfare states are much more likely under fiat money and the redistribution goes from native taxpayers to illegal immigrants. Thus, under fiat money, open borders end up being an open wound by which the productive lifeblood of the country bleeds out, despite the theoretical trade-efficiency benefits. As libertarians like to say, open borders and the welfare state don’t mix. In this article, we’ll examine the other sacred cow of libertarian thought: free trade.Free Trade without Libertarian Ideals
 Free trade is very similar to free movement of labor in that it works great in theory, but not in practice, especially under fiat money. In a libertarian free-market world, free trade works. But that assumes a whole host of libertarian ideals like sound money, non-interfering governments, and minimal aggression. Once those ideals are violated, such as with government intervention in the market, similar moral hazards and long-term costs come with them, making free trade about as libertarian as a fractional reserve bank.
Free trade is very similar to free movement of labor in that it works great in theory, but not in practice, especially under fiat money. In a libertarian free-market world, free trade works. But that assumes a whole host of libertarian ideals like sound money, non-interfering governments, and minimal aggression. Once those ideals are violated, such as with government intervention in the market, similar moral hazards and long-term costs come with them, making free trade about as libertarian as a fractional reserve bank.An example will illustrate what I’m talking about. Let’s say Portugal subsidizes their wine for export to other countries. The obvious first-order effect is that it makes Portuguese wine cheaper in France, perhaps undercutting the price of French wine. Libertarians would say, that’s great! French customers get cheaper goods, so what’s the problem?
As with any government intervention, there are significant second- and third-order effects in play. Subsidization puts unsubsidized companies at risk, perhaps driving them to bankruptcy. In this case, this might be a French wine maker. Subsidized companies may become zombies instead of dying out. In this case, this might be a Portuguese wine maker that was failing domestically but survives by selling to customers abroad with government subsidies. While French customers benefit in the short run with cheaper prices for wine, they are ultimately hurt because the goods that would have existed without government intervention never come to market. Perhaps French wine makers that went bankrupt were innovating. Perhaps the resources of the zombie Portuguese wine maker would have created something better.
Further, the dependency of French people on Portuguese wine means that something going wrong in Portugal, like a war or subsidy cuts, disrupts the supply and price of wine for France. Now France must meddle in Portugal internationally if it doesn’t want the wine supply to get disrupted. The two countries get entangled in such a way as to become more interventionist internationally. A war involving Portugal now suddenly becomes France’s business and incentivizes military aid or even violence. As usual, the unseen effects of government policy are the most pernicious.
Not Really Free
 In other words, what we call free trade isn’t really free trade. A country exporting to the US may subsidize their products through government intervention, making the product cheaper in the US. This hurts US companies, and they’re forced into choices they never would have had to face without the foreign government intervention. But because the good is crossing borders under the rubric of “free trade,” it’s somehow seen as fair. Of course it’s not, as government intervention distorts the market whether it’s done by our own government or a foreign government.
In other words, what we call free trade isn’t really free trade. A country exporting to the US may subsidize their products through government intervention, making the product cheaper in the US. This hurts US companies, and they’re forced into choices they never would have had to face without the foreign government intervention. But because the good is crossing borders under the rubric of “free trade,” it’s somehow seen as fair. Of course it’s not, as government intervention distorts the market whether it’s done by our own government or a foreign government.So why would a foreign government do this? It gets several benefits through targeted market manipulation. First, it makes its own companies’ products more popular abroad and conversely, makes US companies’ products less popular. This has the dual benefit of growing the foreign government’s firms and shrinking, perhaps bankrupting, the US ones.
Targeted subsidization like this can lead to domination under free trade. It’s not unlike the Amazon strategy of undercutting everyone first and using the monopoly pricing power at scale once everyone else has bankrupted. The global monopoly is tremendously beneficial to the country that has it. Not only is there significant tax revenue over the long term, but also a head start on innovations within that industry and an advantage in production in the adjacent industries around the product.
Second, the manufacturing centralization gives that country leverage geo-politically. A critical product that no one else manufactures means natural alliances with the countries that depend on the product, which is especially useful for smaller countries like Taiwan. Their chip manufacturing industry, holding 60% of global supply (2024), has meant that they’re a critical link for most other countries, and hence, they can use this fact to deter Chinese invasion.
Third, because of the centralization of expertise, more innovations, products, and manufacturing will tend to come within the country. This increased production has cascading benefits, including new industries and national security. China leads the world in drone technology, which undoubtedly has given it an innovation advantage for its military, should it go to war.
Fourth, the capital that flows into the country for investing in the monopolized industry will tend to stay, giving the country more wealth in the form of factories, equipment, and skills. While that capital may nominally be in the hands of foreigners, over time, the ownership of that industry will inevitably transition toward native locals, as the knowledge about how to run such industries gets dissipated within the country.
Currency Devaluation: The Universal Trade Weapon
 It would be one thing if only a specific industry were singled out for government subsidies and then the products dumped into the US as a way to hurt US companies, as that would limit the scope of the damage. But with currency devaluation, a government can subsidize all of its exports at the same time. Indeed, this is something that many countries do. While short-term, this helps US consumers, it hurts US companies and forces them into decisions that aren’t good for the US.
It would be one thing if only a specific industry were singled out for government subsidies and then the products dumped into the US as a way to hurt US companies, as that would limit the scope of the damage. But with currency devaluation, a government can subsidize all of its exports at the same time. Indeed, this is something that many countries do. While short-term, this helps US consumers, it hurts US companies and forces them into decisions that aren’t good for the US.To compete, they have to lower costs by using the same devalued currency to pay their labor as their foreign competition. That is, by relocating their capital, their manufacturing, and even their personnel to the country that’s devaluing the currency. Not only does relocating reduce labor cost, but it also often gets them benefits like tax breaks. This makes US companies de facto multinationals and not only makes them subject to other jurisdictions, but ultimately divides their loyalties. To take advantage of the reduced labor, capital must move to another country and, along with it, future innovation.
Such relocations ultimately leave the company stripped of their manufacturing capability in the US, as local competition will generally fare better over the long run. Much of the value of the industry then is captured by other governments in taxes, development, and even state-owned companies. Free trade, in other words, creates a vulnerability for domestic companies as they can be put at a significant disadvantage compared to foreign counterparts.
Hidden Effects of Foreign Intervention
Unlike the multinationals, small companies have no chance as they’re not big enough to exploit the labor arbitrage. And as is usual in a fiat system, they suffer the most while the giant corporations get the benefits of the supposed “free trade”. Most small companies can’t compete, so we get mostly the bigger companies that survive.
The transition away from domestic manufacturing necessarily means significant disruption. Domestic workers are displaced and have to find new work. Factories and equipment either have to be repurposed or rot. Entire communities that depended on the manufacturing facility now have to figure out new ways to support themselves. It’s no good telling them that they can just do something else. In a currency devaluation scenario, most of the manufacturing leaves and the jobs left are service-oriented or otherwise location-based, like real estate development. There’s a natural limit to location-based industries because the market only grows with the location that you’re servicing. Put another way, you can only have so many people give haircuts or deliver packages in a geographic area. There has to be some manufacturing of goods that can be sold outside the community, or the community will face scarce labor opportunities relative to the population.
You also can’t say the displaced workers can start some other manufacturing business. Such businesses will get out-competed on labor by the currency-devaluing country, so there won’t be much investment available for such a business, and even if there were, such a business would be competing with its hands tied behind its back. So in this scenario, what you end up with are a large pool of unemployed people whom the state subsidizes with welfare.
So when a US company leaves or goes bankrupt due to a foreign government’s subsidies, the disruption alone imposes a significant short-term cost with displaced labor, unused capital goods, and devastated communities.
Mitigations
So how do countries fight back against such a devastating economic weapon? There are a few ways countries have found around this problem of currency devaluation under free trade. First, a country can prevent capital from leaving. This is called capital controls, and many countries, particularly those that manufacture a lot, have them. Try to get money, factories, or equipment out of Malaysia, for example, and you’ll find that they make it quite difficult. Getting the same capital into the country, on the other hand, faces few restrictions. Unfortunately, the US can’t put in capital controls because dollars are its main export. It is, after all, the reserve currency of the world.
Second, you can compete by devaluing your own currency. But that’s very difficult because it requires printing a lot of dollars, and that causes inflation. There’s also no guarantee that a competing country doesn’t devalue its currency again. The US is also in a precarious position as the world’s reserve currency, so devaluing the currency more than it already does will make other holders of the dollar less likely to want to hold it, threatening the reserve currency status.
So the main two mitigations against currency devaluation in a free trade scenario are not available to the US. So what else is there? The remaining option is to drop free trade. The solution, in other words, is to add tariffs. This is how you can nullify the effects of foreign government intervention, by leveling the playing field for US manufacturers.
Tariffs
 One major industry that’s managed to continue being manufactured in the US despite significant foreign competition is cars. Notably, cars have a tariff, which incentivizes their manufacture in the US, even for foreign car makers. The tariff has acted as a way to offset foreign government subsidies and currency debasement.
One major industry that’s managed to continue being manufactured in the US despite significant foreign competition is cars. Notably, cars have a tariff, which incentivizes their manufacture in the US, even for foreign car makers. The tariff has acted as a way to offset foreign government subsidies and currency debasement.The scope of this one industry for the US is huge. There are around 300,000 direct jobs in auto assembly within the US (USTR) and there are an additional 3 million jobs supplying these manufacturers within the US. But the benefits don’t end there. The US is also creating a lot of innovation around cars, such as self-driving and plug-in electric cars. There are many countries that would love to have this industry for themselves, but because of tariffs, auto manufacturing continues in the US.
And though tariffs are seen as a tax on consumers, US car prices are cheap relative to the rest of the world. What surprises a lot of people when they move from the US to other countries is finding out that the same car often costs more abroad (e.g. 25% tariffs keep U.S. prices 20% below Europe’s $40K average, 2024). The downside of tariffs pales next to the downsides of “free trade.”
Free Trade Doesn’t Work with Fiat Money
The sad reality is that while we would love for free trade to work in the ideal libertarian paradise, it won’t in our current fiat-based system. The subsidization by foreign governments to bankrupt US companies or to make them multinational, combined with the unfortunate reality of the US dollar being the world reserve currency, means that free trade guts the US of manufacturing. Tariffs are a reasonable way to protect US manufacturers, particularly smaller ones that can’t go multinational.
What’s more, tariffs make the US less fragile and less dependent on international supply chains. Many of the wars in the past 60 years have been waged because of the entanglements the US has with other countries due to the reliance on international supply chains. Lessening this dependency, if only to prevent a war, has clear value.
Lastly, labor has been devalued significantly by fiat monetary expansion, but at least some of that can be recovered if tariffs create more manufacturing, which in turn adds to the demand for labor. This should reduce the welfare state as more opportunities are made available and fewer unemployed people will be on the rolls.
Conclusion
Fiat money produces a welfare state, which makes open borders unworkable. Fiat money also gives foreign governments a potent economic weapon to use against US companies, and by extension the labor force that powers them. Though currency debasement and capital controls are available to other countries as a defense, for the US, neither of these tools is available due to the fact that the dollar is the world reserve currency. As such, tariffs are a reasonable defense against the fiat subsidization of foreign governments.
-
 @ df478568:2a951e67
2025-03-08 02:16:57
@ df478568:2a951e67
2025-03-08 02:16:57I began using/testing Cashu over 105,120 blocks ago when @NVK said "Cashu is very interesting.".
 The first time I swapped sweet cipher-text to sats, it was too new new and novel to digest. Someone sent me cashu over nostr, straight to my npub. I copy pasta-ed it into my minibits wallet and recieved 10 sats. In retrospect, I would compare it to gold backed paper currency. Over a century ago, paper USD was a coupon for gold, "redeemable in gold on demand at the United States Treasury, or in gold for lawful money at any federal reserve bank.
The first time I swapped sweet cipher-text to sats, it was too new new and novel to digest. Someone sent me cashu over nostr, straight to my npub. I copy pasta-ed it into my minibits wallet and recieved 10 sats. In retrospect, I would compare it to gold backed paper currency. Over a century ago, paper USD was a coupon for gold, "redeemable in gold on demand at the United States Treasury, or in gold for lawful money at any federal reserve bank.
In the analog days of the early 20th century a bean-counter at a Federal Reserve bank would give you approximately 5 ounces of gold for an analog bored ape, Ben Franklin. Cashu is an NFT without the jpeg and the innate ability to be redeemed for bitcoin over the lightning network. I've heard NVK describe it as "an honest shitcoin" and I like this framing. The rug-pull risk is greater than zero, but less than the rug-pull risk of Wallet of Satoshi with the added benefit of generational wealth.
This means we can abstract bitcoin value into something that looks like this.
cashuBpGFteCJodHRwczovL21pbnQubWluaWJpdHMuY2FzaC9CaXRjb2luYXVjc2F0YXSBomFpSABQBVDwSUFGYXCCpGFhAmFzeEBkMzM2Mjk1OTZhNTVkODcyNWFjOGI3MDQyNjM5MjQ0OTU4YmJlMjVkYmFhYzIyY2E5Y2M2NTMyNTM1OWFiZDI2YWNYIQNOrrDCFnYa3sMJxpr02o8Bg5AfibjqIOTmiktqYkABKWFko2FlWCBdC0gEM2j5YE4_xMGyuvLHIufqx7zzp6TNJAeJiB6_WmFzWCDRMyyGRmJPYmwB3u8kB7fyBlvRm69hC2DfkyY5Mizd-WFyWCB_88znXGBc_GgRngr9m1nEYAJEDUkQiQLT1e6R9_Un_aRhYQhhc3hANjVkYWQyM2ExNjQyNTYzMDU5OGRmMTdiNDc0YWQ0YzdhMjNhMmFiZjUwNjEzYTdjOTI4NzllMDllZTg5ODcxZWFjWCECoRg-ub_wReP4T6A0UuwqS36Iw6Ton4U5j6IJrLYjKCxhZKNhZVggmXDv_na1XQU3ESYq147mIyDyQm5mgsnkl7HxBbVmXv9hc1ggIbKkVVdG06hBgAvWBhoFo8T-V6MjNzxUGNaGjQjU2e5hclggAJp2vzdgwmehnhwmmFQsZ_BNTb8Aqz_ItwOx0iLQ9NlhZHgtQ29uZ3JhdHVsYXRpb25zIGZvciBjbGFpbWluZyB0aGlzIGVjYXNoIGZpcnN0The lightning network is cool, but requires the reciever to have a wallet. Many Americans began using nostr when Wallet of Satoshi was available to them. They disappeared like a magiian once Wallet of Satoshi was removed from the app stores. To be fair, it still works. Last I checked, sats from wallet of satoshi can still be received and spent from US based IP addresses, but non-technical noobs can no longer download it from app stores designed for the neuro-typical.
I sprinkled a little e cash in a few Substack articles, but few people know what it is. These things takes time. Maybe it's too early. Maybe, just maybe, we can make paper cash great again.
Is it a long shot? Sure. Will I try it anyway? Hell yes!
How To Make Paper Money Great Again
The plan: Create paper products with QR codes that have Cashu. Think tip cards or birtday cards designed to hold cash. You can choose your mint on Mibibits or Macadamia depending on your pnone. This is not bitcoin for posterity. We're talking about pocket spending money, not generational wealth.
I plan to make and sell greeting cards: HallMarc cards.😉 I draw like I'm 5, but we'll let the market decide if they prefer my Kidnergarden-style art or Ideogram. Then I'll write some cheesy words people like on greeting cards. Here's my first idea.
Happy Birthday
Stack Sats.
Okay....So it's more like a first draft, but this is a proof of concept. Cut me some slack. 😅 There's still a few kinks to work out, but here's the prototype.
Set Up Shop With A Free And Open Source Version
I will add these cards to my merch shop. I can add 1,000 sats, maybe some custom amounts, but I'll also open source them. I like to give cards that pay bitcoin to kids in my family. If I open source this, maybe more people will be willing to give the kids in their family sats. It only costs card stock paper, ink, and the sats you give away.
If you're like me, your family knows your a bitcoin dork anyway. We might as well show them it's not just an investment. It's money we can give them they can either save or spend.
We should mention it's better to save bitcoin. That's what stacking sats means. That will be my second draft.
Happy Birthday.
Save as much bitcoin as you can.
Npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0
https://mempool.marc26z.com/block/000000000000000000001567ce65dab25358bcae86c2c573984888eb08948b65
https://marc26z.com/merch/
-
 @ 6e0ea5d6:0327f353
2025-03-08 01:31:14
@ 6e0ea5d6:0327f353
2025-03-08 01:31:14💀
No one returns the same after witnessing such great disrespect that even the eyes doubt what they see.
When behavior does not match the promise, when the path being followed contradicts our principles, when a lie unfolds right before our eyes, or when an offense is deliberately crafted as a test of our resolve, a feeling arises—one that urges us to intervene, to stop such foolishness so that things may proceed as they should. But it is an arrow already released. It cannot be retrieved. There is no turning back. And perhaps, Nietzsche’s words explain it best:
"I’m not upset that you lied to me; I’m upset that from now on, I can’t trust you."
This is what we feel, in conflict with what we know. But maturity has taught us whom to listen to. The mind knows that one must be cruel to oneself so that others will not be cruel to us.
It takes cruelty to kill with indifference what desires to live in our hearts.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 6e0ea5d6:0327f353
2025-03-08 01:17:35
@ 6e0ea5d6:0327f353
2025-03-08 01:17:35Ascolta bene, amico mio. Are you really concerned about what a morally bankrupt society has to say about "being a man"?
The same society that glorifies weakness, where anyone—without the slightest idea of what it means to bear the weight of masculinity—thinks they have the right to an opinion? And, of course, we can’t forget the spectacle: women without any solid paternal reference, never having experienced what it means to have a true masculine figure, now feel entitled to dictate how you should live, act, and even feel. This is more than a joke—it’s the tragic portrait of a civilization on the brink of collapse.
Think about it: it’s as if someone who has never held a hammer tried to teach a blacksmith how to forge steel. What do they know about the burden of being a man? They have never had to carry this weight. They have never known what it is to walk alone, facing the world without guarantees, without anyone to catch them when everything falls apart. Talking is easy, amico mio, when they’ve never had to get their hands dirty with the brutal reality we face every day.
Want to know what you should do? Ignore it. Simple as that. The opinion of those who have never walked your path holds no value. Do not take seriously the judgments of those trapped in a modern fantasy of masculinity, shaped by empty ideals that only encourage weakness. If these women have never had a strong father figure, a real example of masculinity, what do they know about being a man? Nothing. And the worst part: they don’t even realize the emptiness of their words.
And here’s the lesson: you don’t need the approval of a lost society that doesn’t understand the value of discipline, strength, and the sacrifice that true masculinity demands. You don’t need to be shaped by the expectations of this dying world. The only respect that matters is the one you have for yourself. Once you understand this, the judgment of others becomes irrelevant, and their voices fade into the wind like an insignificant breeze.
Who do you want to be respected by? A society that glorifies mediocrity? Or by those who, like you, know the true struggle?
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 4925ea33:025410d8
2025-03-08 00:38:48
@ 4925ea33:025410d8
2025-03-08 00:38:481. O que é um Aromaterapeuta?

O aromaterapeuta é um profissional especializado na prática da Aromaterapia, responsável pelo uso adequado de óleos essenciais, ervas aromáticas, águas florais e destilados herbais para fins terapêuticos.
A atuação desse profissional envolve diferentes métodos de aplicação, como inalação, uso tópico, sempre considerando a segurança e a necessidade individual do cliente. A Aromaterapia pode auxiliar na redução do estresse, alívio de dores crônicas, relaxamento muscular e melhora da respiração, entre outros benefícios.
Além disso, os aromaterapeutas podem trabalhar em conjunto com outros profissionais da saúde para oferecer um tratamento complementar em diversas condições. Como já mencionado no artigo sobre "Como evitar processos alérgicos na prática da Aromaterapia", é essencial ter acompanhamento profissional, pois os óleos essenciais são altamente concentrados e podem causar reações adversas se utilizados de forma inadequada.
2. Como um Aromaterapeuta Pode Ajudar?

Você pode procurar um aromaterapeuta para diferentes necessidades, como:
✔ Questões Emocionais e Psicológicas
Auxílio em momentos de luto, divórcio, demissão ou outras situações desafiadoras.
Apoio na redução do estresse, ansiedade e insônia.
Vale lembrar que, em casos de transtornos psiquiátricos, a Aromaterapia deve ser usada como terapia complementar, associada ao tratamento médico.
✔ Questões Físicas
Dores musculares e articulares.
Problemas respiratórios como rinite, sinusite e tosse.
Distúrbios digestivos leves.
Dores de cabeça e enxaquecas. Nesses casos, a Aromaterapia pode ser um suporte, mas não substitui a medicina tradicional para identificar a origem dos sintomas.
✔ Saúde da Pele e Cabelos
Tratamento para acne, dermatites e psoríase.
Cuidados com o envelhecimento precoce da pele.
Redução da queda de cabelo e controle da oleosidade do couro cabeludo.
✔ Bem-estar e Qualidade de Vida
Melhora da concentração e foco, aumentando a produtividade.
Estímulo da disposição e energia.
Auxílio no equilíbrio hormonal (TPM, menopausa, desequilíbrios hormonais).
Com base nessas necessidades, o aromaterapeuta irá indicar o melhor tratamento, calculando doses, sinergias (combinação de óleos essenciais), diluições e técnicas de aplicação, como inalação, uso tópico ou difusão.
3. Como Funciona uma Consulta com um Aromaterapeuta?

Uma consulta com um aromaterapeuta é um atendimento personalizado, onde são avaliadas as necessidades do cliente para a criação de um protocolo adequado. O processo geralmente segue estas etapas:
✔ Anamnese (Entrevista Inicial)
Perguntas sobre saúde física, emocional e estilo de vida.
Levantamento de sintomas, histórico médico e possíveis alergias.
Definição dos objetivos da terapia (alívio do estresse, melhora do sono, dores musculares etc.).
✔ Escolha dos Óleos Essenciais
Seleção dos óleos mais indicados para o caso.
Consideração das propriedades terapêuticas, contraindicações e combinações seguras.
✔ Definição do Método de Uso
O profissional indicará a melhor forma de aplicação, que pode ser:
Inalação: difusores, colares aromáticos, vaporização.
Uso tópico: massagens, óleos corporais, compressas.
Banhos aromáticos e escalda-pés. Todas as diluições serão ajustadas de acordo com a segurança e a necessidade individual do cliente.
✔ Plano de Acompanhamento
Instruções detalhadas sobre o uso correto dos óleos essenciais.
Orientação sobre frequência e duração do tratamento.
Possibilidade de retorno para ajustes no protocolo.
A consulta pode ser realizada presencialmente ou online, dependendo do profissional.
Quer saber como a Aromaterapia pode te ajudar? Agende uma consulta comigo e descubra os benefícios dos óleos essenciais para o seu bem-estar!
-
 @ dc4cd086:cee77c06
2025-03-07 22:32:02
@ dc4cd086:cee77c06
2025-03-07 22:32:02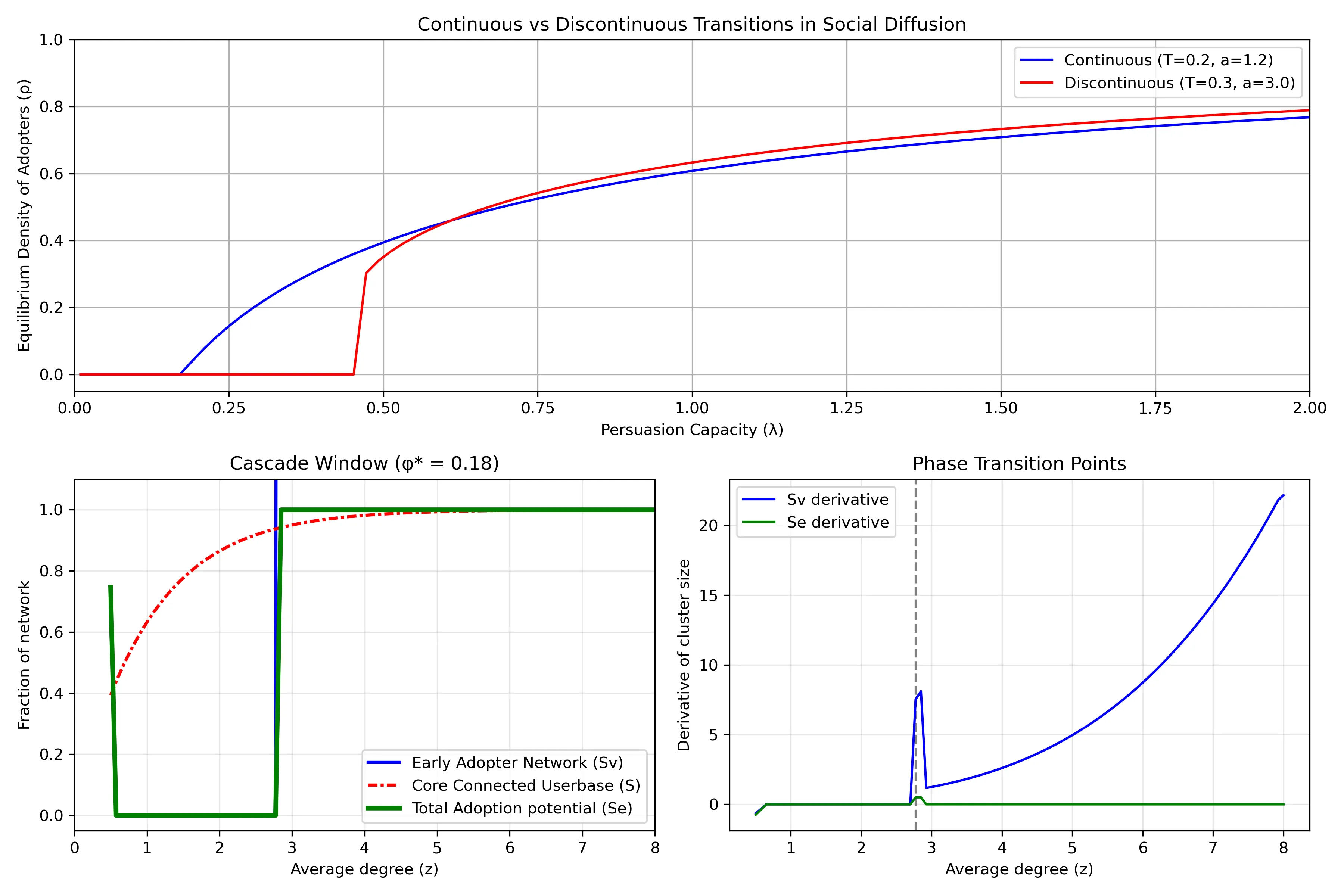
Understanding Network Dynamics in Technology Adoption
- Top Row: Continuous vs Discontinuous Transitions in Social Diffusion
- Shows two different ways that innovations spread through a population. The horizontal axis (
λ) represents "persuasion capacity" - how effectively adopters convince others to join. The vertical axis (ρ) shows what fraction of the population eventually adopts. - Blue line shows a continuous transition: as persuasion capacity increases, adoption grows gradually and smoothly. Example: streaming services that steadily gains users year after year.
- Red line shows a discontinuous transition (or "tipping point"): adoption remains near zero until reaching a critical threshold, then suddenly jumps to a high level. This represents technologies that spread explosively once they reach a critical mass.
- The different curves emerge from the situations of how people make adoption decisions. When there is higher adoption resistance (higher threshold
Tand steeper response curvea), discontinuous transitions become more likely.
Bottom Left: Cascade Window
When is widespread adoption possible? Its based on network structure. The horizontal axis (
z) represents network connectivity - on average, how many connections does an individual have? The plot has a regime "cascade window" - widespread adoption only occurs within a specific range of connectivity: - If connectivity is too low (left side), the network is too fragmented for innovations to spread widely - If connectivity is too high (right side), people become resistant to change because they need many of their connections to adopt before they will follow suitThe different curves show theoretical predictions for:
- The early adopter network (blue solid): people who can be convinced to adopt with minimal influence.
- The core connected userbase (red line): the largest interconnected population in the network
- Total adoption potential (green line): the potential total reach possible through both early adopters and those they influence
Bottom Right: Phase Transition Points
This plot highlights
critical thresholdswhere the system undergoes dramatic changes. The peaks represent points where small changes in network connectivity cause the largest shifts in adoption patterns. The vertical dashed line marks a critical connectivity value where adoption dynamics fundamentally change. Near these critical points, the network becomes especially sensitive - like how a small price drop might suddenly make a product accessible to a much larger market segment, increasing how easily individuals are connected.The green line (total adoption potential rate) shows only a brief spike at the critical threshold and then quickly returns to zero. Implying that the total potential reach of an innovation changes only at that specific critical point and then stabilizes. This is why timing market entry is so crucial - there's a narrow window where network conditions can suddenly enable widespread adoption, and missing this window means the technology might never achieve its full potential.
Further Reading:
- Malcom Gladwell's Tipping Point
Sources:
- https://www.frontiersin.org/journals/physics/articles/10.3389/fphy.2018.00021/full
-
https://www.pnas.org/doi/10.1073/pnas.1414708112
-
https://www.pnas.org/doi/10.1073/pnas.082090499
-
 @ 21ffd29c:518a8ff5
2025-03-07 20:56:56
@ 21ffd29c:518a8ff5
2025-03-07 20:56:56Once upon a time, there was a little boy named Jimmy who had been feeling very sick. He complained about the pain in his throat and nose. His parents tried everything to help him but nothing worked. One day, Jimmy's friend Jeeves came over to visit. He saw that his friend was trying to make something special for his family, and he decided to try home-brewed vaccines as well. Jeeves started experimenting with the homemade vaccine concoctions and made a couple of them. They were very good at making people feel better quickly. One day, Jimmy's parents asked Jeeves if they could have some of these home-made vaccines too. Jeeves agreed, but he had to be careful not to break his blender because it was quite small. The next day, Jeeves brought a mixture of eggs and sheep off the roof of his house, which made him very happy. He started trying them out, and they worked great! Jimmy's parents were so proud of their son for doing something like this. They thanked Jeeves for making such a great home-made vaccine. Jeeves then told Jimmy about how he had found a way to make the blender work again. That was exciting for everyone! The next day, they all tried the homemade vaccines again and made a lot of people feel better quickly too! He decided to make some extra batches of home-made vaccines for everyone who had asked if they could have one too! This was such a fun story! It made everyone feel so happy and excited, and they all wanted -
 @ ec9bd746:df11a9d0
2025-03-07 20:13:38
@ ec9bd746:df11a9d0
2025-03-07 20:13:38I was diving into PoW (Proof-of-Work) once again after nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq3wamnwvaz7tmjv4kxz7fwdehhxarj9e3xzmny9uqzqj8a67jths8euy33v5yu6me6ngua5v3y3qq3dswuqh2pejmtls6datagmu rekindled my interest with his PoW Draw project. It was a fun little trifle, but it shifted my focus just the right way at the right time.
Because then, on Friday, came the Oval Office Travesty. Once I got over the initial shock, I decided I couldn't just curse and lament; I needed to do something bigger, something symbolic, something expressive. So that's exactly what I did—breaking nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcqyqewrqnkx4zsaweutf739s0cu7et29zrntqs5elw70vlm8zudr3y2t9v7jg's record which he held for almost 2 and half years.
Here is a note with PoW 45, the highest PoW known to Nostr (as of now).
nostr:nevent1qvzqqqqqqypzpmym6ar92346qc04ml08z6j0yrelylkv9r9ysurhte0g2003r2wsqy88wumn8ghj7mn0wvhxcmmv9uqsuamnwvaz7tmwdaejumr0dshsqgqqqqqqqqqy8t8awr5c8z4yfp4cr8v7spp8psncv8twlh083flcr582fyu9
How Did I Pull It Off?
In theory, quite simple: Create note, run PoW mining script & wait.
Thanks to PoW Draw, I already had mining software at hand: nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcqyqvqc5tlvn6etv09f0fvuauves49dvgnukjtzsndfv9y8yyrqyxmz7dty6z's notemine_hw, but when you know that there is a 1 in 2^45 chance that the next hash will be the correct one you want to increase the odds a bit. So on Monday evening, I started my Note Mining operation on an old 40 thread machine called Workhorse.
Issues Along the Way
I was immediately surprised that Workhorse (2× Intel Xeon Silver 4114) produced only about 3Mh/s. A laptop (Intel Core i7-1185G7) with Windows and all the bloat did 5Mh/s. That was strange.
Another hurdle was that notemine_hw does not refresh the
created_atfield. With just a few Mh/s of power I was potentially looking at weeks of computation, by then the note would be quite stale. So I created systemd service leveraging theRuntimeMaxSecoption to periodically restart every 3600 seconds assuring that the Note would be max 1 hour old at the time of publishing.Luckily PoW is that kind of problem where every hash attempt is an independent event, so the chance of success is the same whether you do it in small increments or one uninterrupted stretch. So by restarting the mining process I was only losing a few mere seconds every hour due to the overhead.
Once the note staleness issue was resolved, I looked at the 40 workers on Workhorse vs. 7 workers on the laptop and start messing around with running one instance with 40 workers and running 40 instances with 1 worker and found out, that the workers are not bound to a CPU thread and are jumping between the CPUs like rabbits high on Colombian carrots.
The solution? Running multiple instances with one worker each as a service locked to its own CPU core using systemd's
CPUAffinityoption. ``` $aida@workhorse:systemd/system $ sudo cat notemine@.service [Unit] Description=Notemine HW Publish (restarts hourly)[Service] Type=simple CPUAffinity=%i
The command to run:
ExecStart=/home/aida/.cargo/bin/notemine_hw publish --n-workers 1 --difficulty 45 --event-json /home/aida/note.json --relay-url 'wss://wot.shaving.kiwi' --nsec nsec0123456789abcdef
Let the process run for 1 hour (3600 seconds), then systemd will stop it:
RuntimeMaxSec=3600 TimeoutStopSec=1
Tells systemd to restart the service automatically after it stops:
Restart=always RestartSec=1
run as a non-root user:
User=aida Group=aida
[Install] WantedBy=multi-user.target ``` Then I added a starting service to spawn an instance for each CPU thread.
``` $aida@workhorse:systemd/system $ sudo cat notemine_start.service [Unit] Description=Start all services in sequence with 3-second intervals
[Service] Type=oneshot ExecStart=/usr/bin/zsh /home/aida/notemine_start.sh
RemainAfterExit=yes
[Install] WantedBy=multi-user.target
Here is the startup script (I know, loops exist—but Ctrl+C/Ctrl+V is so old-school):aida@workhorse:~ $ cat notemine_start.sh /usr/bin/systemctl start notemine@0.service /usr/bin/sleep 3 /usr/bin/systemctl start notemine@1.service /usr/bin/sleep 3 /usr/bin/systemctl start notemine@2.service /usr/bin/sleep 3 /usr/bin/systemctl start notemine@3.service /usr/bin/sleep 3 ... ... ... /usr/bin/systemctl start notemine@38.service`` The sleep there is critical to make sure that thecreated_at`timestamps are different, preventing redundant hashing.This adjustment made Workhorse the strongest machine in my fleet with 10+Mh/s.
The Luck Aspect
From Monday evening, I started adding all machines at my disposal into the fleet and by Wednesday evening I was crunching hashes on about 130 CPU threads (a lot of them were quite antique) and at the peak was just little shy of 40Mh/s. To compensate for the slow start with the few above-mentioned hiccups and the fact that I had to use my desktop to do other things from time to time, I counted with the conservative estimate of 30Mh/s when I was doing all the probability calculations.
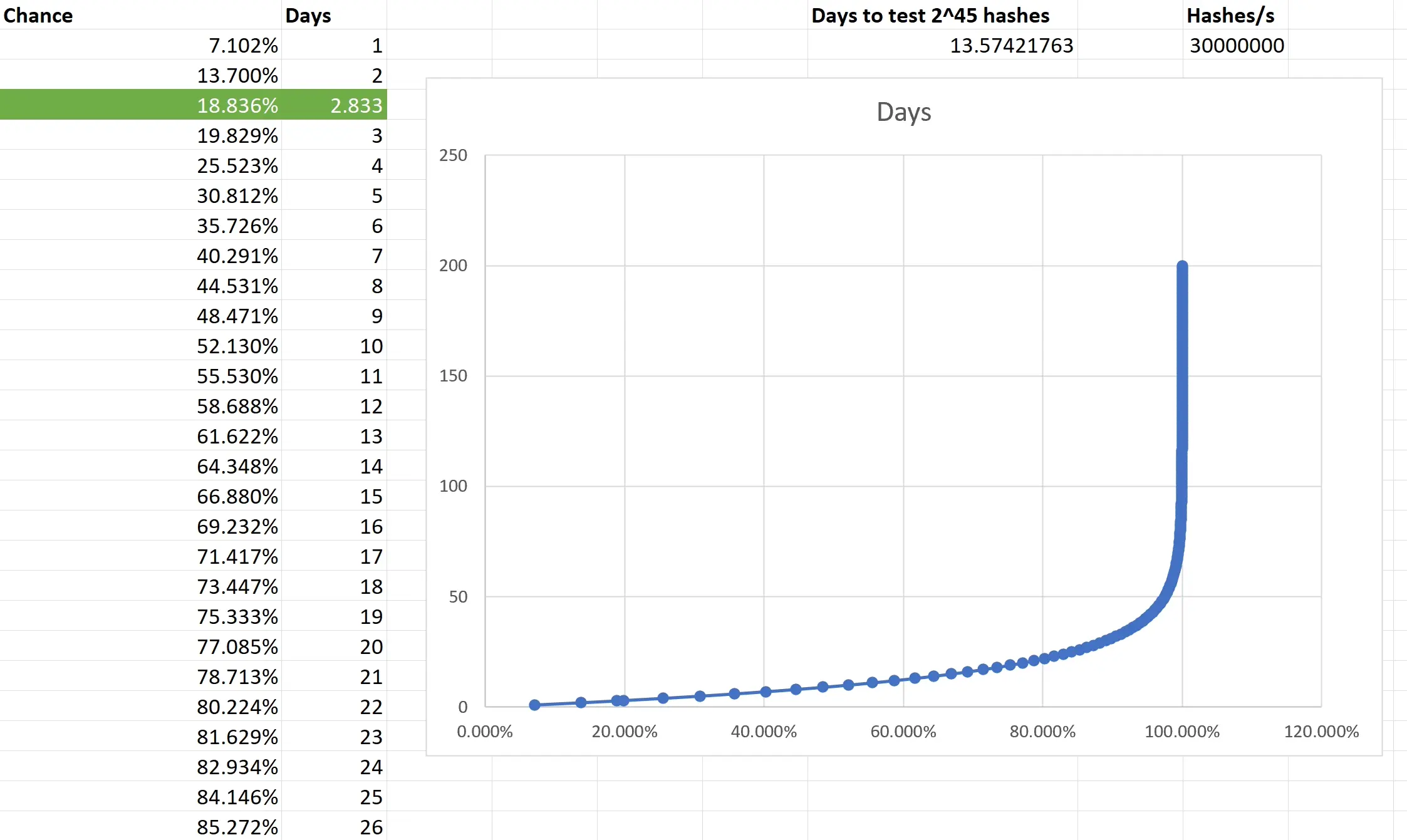
Based on the type of task that PoW mining is, the outcome is not predictible. You are only looking at what is the chance that the outcome of every single independent event will be consecutively non-favourable and then subtracting it from 1 to get the chance of that single favourable event you want. I really had to brush up on my combinatorics and discrete mathematics to make sure I have at least an elementary understanding of what is going on. Also, because we are not just throwing a dice 5 times, but are operating with big numbers, approximation was necessary. Luckily, the formula is available and quite simple in the end.
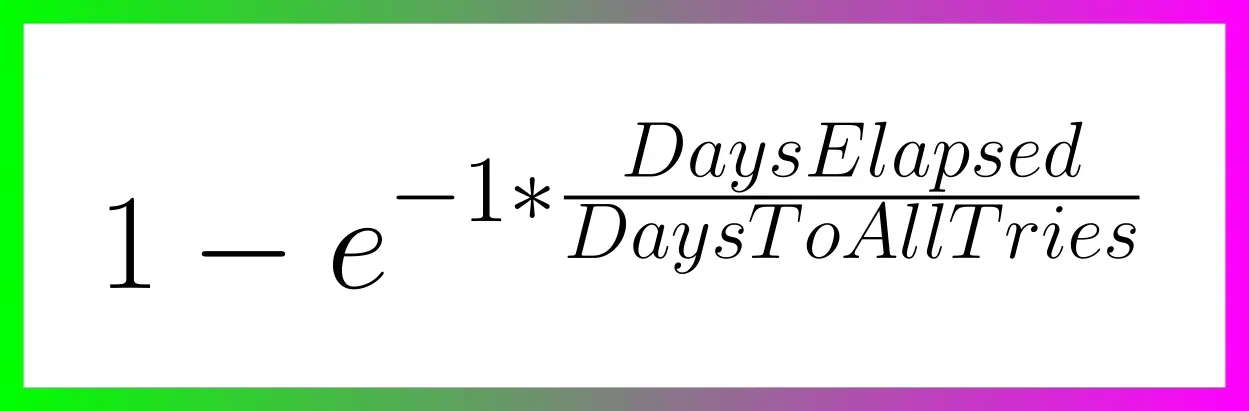
Two weeks to exhauste all the possible tries still doesn't guarantee anything, actually there is a slighlty less than 2 in 3 chance that you will have a result after all that time. So the fact that I was able to hit the right hash in less than 3 days was good luck. Not insane lottery winning luck, but good luck; slighlty lower than 1 in 5.
Do you want to beat me?
Go ahead! All the pitfalls are described above and until there is a GPU-based PoW Mining available, we are all on pretty even ground.
Do you hate the note?
In that case, feel free to enjoy this accompanying image:

-
 @ d058ffb7:70ed2330
2025-03-07 19:45:59
@ d058ffb7:70ed2330
2025-03-07 19:45:59Au cours de mon éternelle recherche du Graal de l'application de prise de note, je suis récemment tombé sur une recommandation intéressante : LogSeq.
Cette application fait partie de la dernière génération de logicielle pour la prise de note, en facilitant la recherche. Celles-ci se distinguent en offrant la cartographie de pensée (mind map), qui permet de liée différents sujets ensemble, souvent sous la forme d'hyperlien. On peut ensuite les consulter sous forme de graphique de connaissance. Sur le marché, on peut donc comparer Logseq à Roam, Obsidian ou Notion.
Parmi les avantages de cette application, il y a la facilité à explorer les différents sujets de façon cohérente, un peu à la façon Wikipedia, mais également de regrouper des thèmes communs. Elle permet également une grande flexibilité dans la création de contenu. Enfin, la mise en page est basée sur le système de mark-up, ce qui rend saisie simple.
Utilisation
J'ai eu la chance de tester son utilisation durant un voyage récemment afin de le tester avec plusieurs cas d'utilisation. En voici quelques un :
Journal et planification
À l'ouverture, on se retrouve dans une interface qui peut rappeler un journal, i.e. une page par date de calendrier. En plus de pouvoir suivre les notes chronologiquement, cette interface est aussi utile pour la planification, puisque qu'on peut attacher des notes à une date ultérieure (via la fonction \date picker) et voir ces liens quand arrivera la journée prévue.
Liste de points
L'application encourage beaucoup l'utilisation de liste de points. Elle permet alors d'indenter sans limite, mais également d'éclater/fermer les points faciliter la consultation lors beaucoup de sous-points.
Gestion de tâche
Des bonnes vieilles to-do list dont possibles, avec bouton pour biffer les tâches terminées. On peut se limiter à une liste unique et consolidée, mais également répartir les tâches dans les différentes pages en utilisant un lien vers la page principale.
Lecture - Notes, résumés et recommandations
On peut également y collecter les différentes lectures, ainsi que les recommandations reçues. Certains livres pourront alors leur page spécifique lorsqu'un résumé ou des notes sont pertinentes. Il est également possible de maintenir une page de citations et de les lier au livre correspondant. À chacun sa saveur Considérant la flexibilité et que nous avons tous une façon unique de réfléchir, il est important de se donner la chance de découvrir l'outils et de développer sa propre stratégie/structure pour la prise de note, en fonction de sa propre réalité et de ses besoins.
Avantages
Gratuit
Contrairement à plusieurs compétiteurs, la version principale est gratuite pour tous. À l'heure actuelle, elle n'est pas sur le Play Store d'Android, on doit plutôt télécharger et installer le package à partir de leur site web.
Open-source
L'application est disponible sur GitHub et publiée selon la licence AGPL-3.0 license, qui confirme l'aspect open-source, mais qui dont les versions qui en dépendent doivent conserver cette licence (et donc ne peuvent la fermer par la suite). L'application est activement développé, mais bénéficie également d'un nombre impressionnant d'application tierce / plug-in, qui permettent une utilisation encore plus complète.
Défis
Appareils multiples
Malheureusement, LogSeq ne permet toujours pas la synchronisation avec la version principale. Cette fonctionnalité (LogSeq Sync) est présentement en bêta mais n'est disponible que pour les commanditaires et backers. Comme c'est open-source et n'est qu'ultimement un fichier texte, il y a différentes stratégies maison, mais pour l'instant, l'utilisation sur mobile était suffisante. Au besoin, il est possible d'exporter le contenu sous format .json et ensuite l'importer dans une version sur bureau (ce que j'ai fait pour extraire le graphe plus haut).
Prochaines étapes
Applications / Plugins
Il me reste maintenant à explorer le marketplace pour découvrir les nombreux plug-ins disponibles.
De nombreux guides sont disponibles, sur Youtube, mais également sur leur blog et leur page de communauté. Pourquoi ne pas commencer par cette page ?
https://hub.logseq.com/use-cases/1Sr4awszMQzD4GM5KvWim7/10-must-have-plugins-for-logseq/jgDG2ZVkeZGSQHXUNkWroo
-
 @ a296b972:e5a7a2e8
2025-03-07 19:20:32
@ a296b972:e5a7a2e8
2025-03-07 19:20:32Wer soll wehrpflichtig sein? Alle, die einen deutschen Pass haben? Auch die, die durch die Willkommenskultur nach Deutschland gekommen sind? Gleich hier und schon sterben?
Wie groß ist die Bereitschaft „für’s Vaterland“ sein Leben einzusetzen? Die Messer-Fachkräfte und Autofahrer unter den Willkommenen könnten einen Vorteil gegenüber den Bio-Deutschen haben. Mehr Testosteron, mehr Cochones!
Gibt es noch bewohnbare Kasernen? Wenn ja, wer wohnt derzeit in ihnen und wohin mit denen? Entsprechen sie der Brandschutz-Verordnung? Heizen sie mit Wärmepumpen?
Wie gut wird die Unterbringung unterschiedlicher Kulturen, Ethnien und Religionszugehörigkeiten in den Kasernen lebenspraktisch funktionieren?
Werden separate Küchen eingerichtet, damit die verschiedenen Kulturen und Religionen ihrer Herkunft nach entsprechende Kost zubereitet bekommen? Ich kann mir nicht vorstellen, dass Erbsensuppe mit Schweins-Bockwurst aus der Gulaschkanone die Leibspeise für alle Migranten werden wird. Und es muss mindestens ein veganes und ein glutenfreies Essen zur Auswahl geben. Allergien können sonst die Wehrkraft zersetzen. Gutes Essen ist wichtig für die Truppenmoral!
Vereintes Duschen, Toilettengang kein Problem? Sind Kampfunterbrechungen für Gebete vorgesehen? Werden Gebetsteppiche in Tarnfarben angeschafft?
Werden die Pass-Straßen in den Zelten der ehemaligen Impf-Zentren für die mRNA-Vergiftung zu Kreiswehr-Ersatz-Ämtern umfunktioniert. Mit Länderfähnchen für die vielen Nationen?
Werden in der Volkshochschule Schnellkurse für Ausbilder angeboten?
Wie steht es um die Moral in der Truppe bei denjenigen, die sich der Genbehandlung unterziehen mussten, und sich damit schon einmal mit ihrem Leben eingesetzt haben?
Wäre es gerecht, wenn alle Menschen mit einem deutschen Pass möglicherweise aufgrund ihrer Herkunft unterschiedlich gut oder weniger gut als wehrtauglich eingestuft würden?
Wie soll die Gleichstellung von Männern und Frauen in der Wehrpflicht umgesetzt werden? Wie wäre diese in den unterschiedlichen Kulturen umzusetzen? Wird garantiert, dass muslimische Frauen weiter ihr Kopftuch tragen können? Gibt es spezielle weibliche Uniformen mit Vollverschleierung?
In wie vielen Sprachen werden Dienstanweisungen mündlich ausgegeben? Und schriftlich in lateinischer und arabischer Schrift?
Wie viele Sprachen müssen Vorgesetzte sprechen, da nicht davon auszugehen ist, dass alle Wehrpflichtigen Deutsch und schon gar nicht Militär-Deutsch verstehen werden? Das gilt sowohl für Bio-Deutsche, als auch für die Menschen mit Migrationshintergrund.
Sind daher Dienst-Handys mit Übersetzer-App vorgesehen? Gäbe es für jeden ein Gerät oder müssen sich Klein-Gruppen jeweils eine Übersetzer-App teilen? Wird ein potenzieller Feind im Ernstfall warten, bis alle Soldaten die Befehle in ihre Sprache übersetzt haben, damit sie wissen, was zu tun ist?
Wird es Sandalen und Flip-Flops mit Stahlkappen geben?
Wird es Helme in Übergröße geben, damit die Hochfrisuren der Drag-Queens nicht zu Schaden kommen?
Ist vorgesehen, dass im Übungsgelände eine Fußbodenheizung verlegt wird, damit es bei Kriech-Übungen den jungen, deutschen Männern nicht zu kalt wird?
Würden Waffen und Munition den Umwelt- und Klima-Vorschriften der Agenda 2030 entsprechen? Gäbe es Gärtner-Kolonnen, die die Abdrücke der Panzerketten, nach Manöver-Übungen und im Ernstfall, wieder einebnen und glattharken, die Bombentrichter zuschütten und die Natur wieder in ihren ursprünglichen Zustand versetzen würden?
Wird jahrelanges virtuelles Ballerspielen auf die Grundausbildungszeit angerechnet?
Wird die deutsche Bevölkerung, die in die Mobilitätsaktivitäten einbezogen werden soll, bereit sein, für durchziehende Truppen Kaffee zu kochen (am liebsten Latte Macchiato extra large, aber bitte mit Hafermilch!) und Leberwurst-Butterbrote zu schmieren? Was, wenn einer statt Kaffee lieber Tee oder eine Bio-Limonade haben möchte, was wenn der Gefreite Malte Alexander statt Leberwurst lieber einen veganen Brotaufstrich vorzieht?
Wird es eine allgemeine Auszahlung einer Versorgungspauschale für die Bevölkerung geben, oder ist es Bürgerpflicht aus Solidarität mit der kämpfenden Truppe die Verköstigung aus der eigenen Tasche zu zahlen? Oder werden die Kosten mit einer Pauschale bei der Einkommensteuer steuersenkend berücksichtigt?
Darf die deutsche Bevölkerung im Ernstfall ausnahmsweise die deutsche Fahne am Balkon hissen, oder ist eine andere Fahne vorgesehen?
Bis all diese Fragen geklärt und durch die deutschen Bürokratie-Mühlen gegangen sind, hat ein potenzieller Feind das Land schon drei Mal überrollt.
Die geplante Merz-Revolution, die Kombination von Militärausgaben und Ausgaben in die Infrastruktur innerhalb der Sondervermögens-Schulden macht Sinn. Auf den maroden Straßen und Brücken in Deutschland können keine schweren Panzer fahren. Und die müssen auch erst einmal gebaut werden. Hier finden ja jetzt die Arbeiter in der niedergehenden Autoindustrie eine „Anschlussverwendung“ in der Rüstungsindustrie.
Laut Fritzefanzler soll die Bundeswehr ungehinderten Zugang zu Schulen und Hochschulen bekommen, um Kanonenfutter zu rekrutieren. Ein paar Lebensmüde werden sich schon finden lassen. Man will ja auch kein Rechter sein, weil man sich sonst als Pazifist outen müsste.
Man kann nur hoffen, dass ein potenzieller Feind so lange wartet, bis alles fertig ist.
Deutschland braucht gar keinen Feind von außen. Mit deutscher Gründlichkeit zerstört sich Deutschland von innen heraus systematisch von ganz alleine. Wer hat sich diesen Plan ausgedacht?
Das wichtigste wurde bei all der deutschen Kriegstüchtigkeit jedoch vergessen: Deutschland braucht einen Feind! Ohne Feind kein Krieg! Russland macht nicht die geringsten Anzeichen, sich hier zur Verfügung stellen zu wollen. Es gibt einfach keinen Grund. Weder von russischer Seite, Frau Baerbock in Brandenburg einen Hausbesuch abzustatten, noch von deutscher Seite, die keinerlei Belege dafür hat, dass Deutschland von irgendwem bedroht wird.
Deutschland inszeniert derzeit ein heraufkommendes Gewitter bei strahlend blauem Himmel. Frankreich erklärt Russland quasi den Krieg und das russische Militär schüttelt vermutlich ratlos mit dem Kopf, weil es sich fragt, warum nur?
Die EU beruft einen Sondergipfel ein. Mit 800 Milliarden Budget präsentiert sie den ReArm-EU-Plan. Es gehen Gerüchte um, dass die USA die NATO verlassen könnten. Europa muss dringend wiederbewaffnet werden. Das Ganze dauert, wenn es denn überhaupt klappt, mindestens 10 bis 15 Jahre. Und in der Zwischenzeit? Kann Frau von der Leyen die Zeit anhalten und wir wissen es nur noch nicht?
Erste Schwierigkeiten tauchen schon auf, weil die eine Nation nicht preisgeben will, wie viele Waffen sie noch im Keller hat, und andere Nationen wollen nicht preisgeben, wie wenig Waffen sie noch in der Garage haben. Was für ein Chaos-Club. Dennoch gut, denn so wird das alles nichts.
Angefeuert in Brüssel von der Waffen-Lobbyistin aus Düsseldorf-Rheinmetall, Herrn Kriegsgewitter, dem Mann aus Bayern mit den unglücklichen Initialen AH und unterstützt von Joschka und dem zukünftigen, hoffentlich bald schon wieder ehemaligen Bundeskanzler.
Europa benimmt sich wie ein aufgeschreckter Haufen gackernder Gänse, die wild hin und her rennen und keine Ahnung haben, was sie tun sollen. Blinder Aktionismus ist angesagt.
Es gibt einfach keine klare Begründung, warum eine Bedrohung sofortige, dringende Maßnahmen nötig macht. Warum nicht? Weil es keinen Grund gibt.
Wie wäre es, statt einer Wehrpflicht, mit einer Pflicht zur Wahrnehmung der Realität, die derzeit offensichtlich auf Heimaturlaub ist. (Ort unbekannt, möglicherweise Planet Vega, Sternbild Leier)? Wohin sind Besonnenheit und Hausverstand verschwunden?
Im Hinblick darauf, dass es durchaus sein kann, dass die USA die NATO wirklich verlassen werden, würde es in der Tat Sinn machen, dass die europäischen Nationen, jede für sich, eine gewisse Verteidigungsfähigkeit mit der Zeit wiederherstellen würde. Nach Abgleich könnte man sogar ein europäisches Militärbündnis schließen, eventuell Reststrukturen der NATO nutzen. Dieser Vorgang würde ebenso gute 10 bis 15 Jahre dauern. In Polen vielleicht schon etwas früher, da wird ja schon seit einiger Zeit kräftig aufgerüstet und die Armee aufgestockt. Manche scheinen es kaum abwarten zu können, sich verstümmeln zu lassen oder zerfetzt zu werden. Viele scheinen wirklich zu glauben, Krieg ist so was wie „Call of Duty“, aber Krieg ist noch ernster als ernst.
In der Zwischenzeit sollte alles darangesetzt werden, größtmögliche Sicherheit für einen langfristigen, andauernden Frieden zu schaffen, statt damit zu drohen, aus Kanonen zu schießen, die man in absehbarer Zeit gar nicht haben wird. Genau das Gegenteil geschieht. Ein weiterer Part aus George Orwells „1984“ soll umgesetzt werden: Krieg ist Frieden. Wie bescheuert kann man sein?
Erst verscherzt es sich Europa mit Russland, jetzt auch noch mit den USA. Merz soll Trump ein Arschloch genannt haben. Trump hat ein Elefanten-Gedächtnis. Der Schuss kann auch ganz leicht nach hinten losgehen. Es gibt da noch so einige Verträge aus der Nachkriegszeit. Und vermutlich gibt es auch die Kanzler-Akte, nach der ein neuer Bundeskanzler in den USA anzutreten hat.
Eine deutsche „Geistesgröße“ hat vor den US-Wahlen sinngemäß gesagt: Nicht auszumalen, wenn Trump die Wahlen gewinnt. Wie stehen wir denn da?
Abgeleitet davon die Frage: Angenommen, Deutschland und Europa hätten es tatsächlich geschafft, innerhalb kürzester Zeit aufzurüsten und der Russe kommt gar nicht. Wie stehen wir denn da?
In beiden Fällen wie die letzten Deppen, die die Verantwortlichen wohl auch sein wollen.
Europa ist größenwahnsinnig geworden, und im schlimmsten Fall, falls die Lage eskaliert, sind die Menschen, die keinen Krieg wollen, wie immer, die Leidtragenden, die mit der Arschkarte.
Gegen Unkenntnis kann man etwas tun, gegen Dummheit kämpfen selbst die Götter vergebens.
Frieden – Mir – Pace – Peace (sowas von rääääääächts!)
-
 @ 401014b3:59d5476b
2025-03-07 14:44:12
@ 401014b3:59d5476b
2025-03-07 14:44:12Alright, football savages, it’s March 2025, and we’re tearing into the AFC North like it’s a pierogi-eating contest at a steel mill tailgate. Free agency’s a wild west shootout, the draft’s a blind bet, and this division’s always a brutal cage match of toughness and trash talk. The Bengals and Ravens duked it out in 2024, the Steelers hung tough, and the Browns… well, they Brownsed. Let’s throw some records on this grinder and see who’s got the grit to claim the crown. Here we go, fam—pass the Iron City.
Cincinnati Bengals: 11-6 – Burrow’s Back with a Vengeance
The Bengals were a force in 2024, and 2025’s shaping up as Joe Burrow’s revenge tour. With Ja’Marr Chase and Tee Higgins (assuming they keep him) torching DBs, this offense is a video game cheat code. The O-line’s finally decent, and the defense—Logan Wilson, Trey Hendrickson—if he stays, brings the pain when it matters. Roster changes are a hurdle—Higgins and Hendrickson might chase a mega-deal elsewhere—but Burrow’s ice-cold clutch factor seals it. 11-6, division champs. Cincy’s ready to remind everyone who dey really are.
Baltimore Ravens: 10-7 – Lamar’s Still a Freak
The Ravens are the AFC North’s relentless machine. Lamar Jackson’s running circles around defenses, Derrick Henry’s still trucking fools (if he’s back), and Zay Flowers keeps the passing game spicy. That defense—Roquan Smith, Kyle Hamilton—is a brick wall, but free agency could bite. Justin Madubuike SHOULD stay, and the secondary’s got holes to patch. 10-7’s the call, snagging a wildcard. They’re a half-step behind Cincy but built to ruin someone’s playoff dreams.
Pittsburgh Steelers: 9-8 – Tomlin’s Eternal .500 Magic
Mike Tomlin’s Steelers are the NFL’s cockroaches—impossible to kill. Russell Wilson initially steadied the ship in 2024, and with Najee Harris pounding the rock and George Pickens stretching the field, they’ve got enough juice. The defense—T.J. Watt, Cam Heyward (if he’s still kicking)—is still a nightmare, but age and free agency loom. Patrick Queen could bolt, the Steelers need to settle on a QB, and the secondary’s thin. 9-8’s classic Tomlin—competitive, scrappy, maybe a wildcard if the stars align. Pittsburgh doesn’t die; it just reloads.
Cleveland Browns: 6-11 – Deshaun’s Last Stand?
The Browns are the AFC North’s punching bag, and 2025 ain’t looking much brighter. Deshaun Watson’s a $230 million question mark—Nick Chubb’s back, Jerry Jeudy’s a weapon, but that O-line’s shaky. The defense—Myles Garrett, Denzel Ward—keeps ‘em in games, but free agency might swipe Jeremiah Owusu-Koramoah, and the vibes are off. 6-11’s the harsh truth—too much baggage, not enough spark. Cleveland’s stuck in neutral ‘til they figure out QB.
The Final Bell
The AFC North in 2025 is a Cincinnati coronation with a bloody chase. The Bengals (11-6) take the title because Burrow’s a killer, the Ravens (10-7) claw a wildcard with Lamar’s wizardry, the Steelers (9-8) hang tough, and the Browns (6-11) wallow. Free agency’s the game-changer—lose a stud, you’re screwed; keep ‘em, you’re cooking. Hit me on Nostr when I butcher this, but this is my AFC North gospel. Let’s roll, degenerates.
-
 @ eac63075:b4988b48
2025-03-07 14:35:26
@ eac63075:b4988b48
2025-03-07 14:35:26Listen the Podcast:
https://open.spotify.com/episode/7lJWc1zaqA9CNhB8coJXaL?si=4147bca317624d34
https://www.fountain.fm/episode/YEGnlBLZhvuj96GSpuk9
Abstract
This paper examines a hypothetical scenario in which the United States, under Trump’s leadership, withdraws from NATO and reduces its support for Europe, thereby enabling a Russian conquest of Ukraine and the subsequent expansion of Moscow’s influence over Eurasia, while the US consolidates its dominance over South America. Drawing on classical geopolitical theories—specifically those of Halford Mackinder, Alfred Thayer Mahan, Rudolf Kjellén, and Friedrich Ratzel—the study analyzes how these frameworks can elucidate the evolving power dynamics and territorial ambitions in a reconfigured global order. The discussion highlights Mackinder’s notion of the Eurasian Heartland and its strategic importance, Mahan’s emphasis on maritime power and control of strategic routes, Kjellén’s view of the state as an expanding organism, and Ratzel’s concept of Lebensraum as a justification for territorial expansion. The paper also explores contemporary developments, such as the US–Ukraine economic agreement and Trump’s overt territorial ambitions involving Greenland and Canada, in light of these theories. By juxtaposing traditional geopolitical concepts with current international relations, the study aims to shed light on the potential implications of such shifts for regional stability, global security, and the balance of power, particularly in relation to emerging neocolonial practices in Latin America.
Introduction
In recent years, the geopolitical dynamics involving the United States, Russia, and Ukraine have sparked analyses from different theoretical perspectives. This paper examines recent events – presupposing a scenario in which Donald Trump withdraws the US from NATO and reduces its support for Europe, allowing a Russian conquest of Ukraine and the expansion of Moscow’s influence over Eurasia, while the US consolidates its dominance over South America – in light of classical geopolitical theories. The ideas of Halford Mackinder, Alfred Thayer Mahan, Rudolf Kjellén, and Friedrich Ratzel are used as reference points. The proposal is to impartially evaluate how each theory can elucidate the developments of this hypothetical scenario, relating Russian territorial expansion in Eurasia to the strategic retreat of the US to the Western Hemisphere.
Initially, we will outline Mackinder’s conception of the Heartland (the central Eurasian territory) and the crucial role of Eastern Europe and Ukraine in the quest for global dominance. Next, we will discuss Mahan’s ideas regarding maritime power and the control of strategic routes, considering the impacts on the naval power balance among the US, Russia, and other maritime powers such as the United Kingdom and Japan. Subsequently, we will examine Kjellén’s organic theory of the state, interpreting the Russian expansionist strategy as a reflection of a state organism in search of vital space. In the same vein, Ratzel’s concept of “Lebensraum” will be explored, along with how Russia could justify territorial expansion based on resources and territory. Finally, the paper connects these theories to the current political context, analyzing the direct negotiations between Washington and Moscow (overlooking Ukraine and Europe), the US policy toward authoritarian regimes in Latin America, and the notion of a hemispheric division of power – the “Island of the Americas” under North American hegemony versus an Eurasia dominated by Russia. Lastly, it considers the possibility that such a geopolitical arrangement may foster the strengthening of authoritarian governments globally, rather than containing them, thus altering the paradigms of the liberal world order.
The Heartland of Mackinder: Ukraine, Eurasia, and Global Dominance
Halford J. Mackinder, a British geographer and pioneer of geopolitics, proposed the celebrated Heartland Theory in the early twentieth century. Mackinder divided the world into geostrategic zones and identified the Heartland—the central continental mass of Eurasia—as the “geographical pivot of history” [5]. His most famous maxim encapsulates this vision: “who rules Eastern Europe commands the Heartland; who rules the Heartland commands the World Island; who rules the World Island commands the world” [5]. Eastern Europe and, in particular, the region of present-day Ukraine, play a key role in this formula. This is because, for Mackinder, Eastern Europe functions as a gateway to the Heartland, providing access to resources and a strategic position for the projection of continental power [5].
Applying this theory to our scenario, the conquest of Ukraine and Eastern European countries by Russia would have profound geopolitical implications. From a Mackinderian point of view, such a conquest would enormously strengthen Russia’s position in the Heartland by adding manpower (population) and Ukraine’s industrial and agricultural resources to its power base [5]. In fact, Mackinder argued that controlling the Heartland conferred formidable geostrategic advantages—a vast terrestrial “natural fortress” protected from naval invasions and rich in resources such as wheat, minerals, and fuels [5]. Thus, if Moscow were to incorporate Ukraine (renowned for its fertile soil and grain production, as well as its mineral reserves) and extend its influence over Eastern Europe, Russia would consolidate the Heartland under its direct control. In this context, the absence of the USA (withdrawn from NATO and less engaged in Europe) would remove an important obstacle to Russian predominance in the region.
With central and eastern Eurasia under Russian influence, it would be possible to move toward the realization of the geopolitical nightmare described by Mackinder for Western maritime powers: a hegemonic continental power capable of projecting power to both Europe and Asia. Mackinder himself warned that if a Heartland power gained additional access to an oceanic coastline—in other words, if it combined land power with a significant maritime front—it would constitute a “danger” to global freedom [5]. In the scenario considered, besides advancing into Eastern Europe, Russia would already possess strategic maritime outlets (for example, in the Black Sea, via Crimea, and in the Baltic, via Kaliningrad or the Baltic States if influenced). Thus, the control of Ukraine would reinforce Russia’s position in the Black Sea and facilitate projection into the Eastern Mediterranean, expanding its oceanic front. From a Mackinderian perspective, this could potentially transform Russia into the dominant power of the “World Island” (the combined mass of Europe, Asia, and Africa), thereby unbalancing the global geopolitical order [5].
It is worth noting that, historically, Mackinder’s doctrine influenced containment strategies: both in the interwar period and during the Cold War, efforts were made to prevent a single power from controlling the Heartland and Eastern Europe. NATO, for example, can be seen as an instrument to prevent Soviet/Russian advances in Europe, in line with Mackinder’s imperative to “contain the Heartland.” Thus, if the USA were to abandon that role—by leaving NATO and tacitly accepting the Russian sphere of influence in Eurasia—we would be witnessing an inversion of the principles that have guided Western policy for decades. In short, under Mackinder’s theory, the Russian conquest of Ukraine and beyond would represent the key for Russia to command the Heartland and, potentially, challenge global hegemony, especially in a scenario where the USA self-restricts to the Western Hemisphere.
The Maritime Power of Mahan and the Naval Balance between West and East
While Mackinder emphasized continental land power, Alfred Thayer Mahan, a nineteenth-century American naval strategist, highlighted the crucial role of maritime power in global dominance. In his work The Influence of Sea Power upon History (1890), Mahan studied the example of the British Empire and concluded that control of the seas paved the way for British supremacy as a world power [10]. He argued that a strong navy and the control of strategic maritime routes were decisive factors for projecting military, political, and economic power. His doctrine can be summarized in the following points: (1) the United States should aspire to be a world power; (2) control of the seas is necessary to achieve that status; (3) such control is obtained through a powerful fleet of warships [17]. In other words, for Mahan, whoever dominates the maritime routes and possesses naval superiority will be in a position to influence global destinies, ensuring trade, supplies, and the rapid movement of military forces.
In the proposed scenario, in which the USA withdraws militarily from Europe and possibly from the Eurasian stage, Mahan’s ideas raise questions about the distribution of maritime power and its effects. Traditionally, the US Navy operates globally, ensuring freedom of navigation and deterring challenges in major seas (Atlantic, Pacific, Indian, etc.). A withdrawal of the USA from NATO could also signal a reduction in its naval presence in the Northeast Atlantic, the Mediterranean Sea, and other areas close to Eurasia. In such a case, who would fill this naval vacuum? Russia, although primarily a land power, has been attempting to modernize its navy and has specific interests—for example, consolidating its dominance in the Black Sea and maintaining a presence in the Mediterranean (with a naval base in Tartus, Syria). The United Kingdom, a historic European maritime power, would remain aligned with the USA but, without American military support in Europe, might potentially be overwhelmed trying to contain an increasingly assertive Russian navy in European waters on its own. Japan, another significant maritime actor allied with the USA, is concerned with the naval balance in the Pacific; without full American engagement, Tokyo might be compelled to expand its own naval power to contain both Russia in the Far East (which maintains a fleet in the Pacific) and, especially, the growing Chinese navy.
According to Mahan’s thinking, strategic maritime routes and choke points (crucial straits and channels) become contested prizes in this power game. With the USA focusing on the Americas, one could imagine Washington reinforcing control over the Panama Canal and Caribbean routes—reviving an “American Gulf” policy in the Western Atlantic and Eastern Pacific. In fact, indications of this orientation emerge in statements attributed to Trump, who once suggested reclaiming direct control over Panama, transforming Canada into a North American state, and even “annexing” Greenland due to its Arctic geopolitical importance [18]. These aspirations reflect a quest to secure advantageous maritime positions near the American continent.
Conversely, in the absence of American presence in the Eastern Atlantic and Mediterranean, Russia would have free rein for regional maritime projection. This could include anything from the unrestricted use of the Black Sea (after dominating Ukraine, thereby ensuring full access to Crimea and Ukrainian ports) to greater influence in the Eastern Mediterranean via Syria and partnerships with countries such as Iran or Egypt. The Baltic Sea would also become an area of expanded Russian interest, pressuring coastal countries and perhaps reducing NATO’s traditional local naval supremacy. However, it is worth noting that even with these regional expansions, Russia lacks a blue-water navy comparable to that of the USA; thus, its initial global maritime impact would be limited without alliances.
An important aspect of Mahan’s theories is that naval power serves as a counterbalance to the land power of the Heartland. Therefore, even if Russia were to dominate the Eurasian continental mass, the continued presence of American naval might on the oceans could prevent complete global domination by Moscow. However, if the USA voluntarily restricts its naval reach to the Americas, it would forgo influencing the power balance in the seas adjacent to Eurasia. Consequently, the balance of maritime power would tend to shift in favor of regional Eurasian actors. The United Kingdom and Japan, traditional allies of the USA, could intensify their naval capabilities to defend regional interests—the United Kingdom safeguarding the North Atlantic and the North Sea, and Japan patrolling the Northwest Pacific—but both would face budgetary and structural limitations in fully compensating for the absence of the American superpower. Consequently, Mahan’s vision suggests that the withdrawal of the USA from the extra-regional scene would weaken the liberal maritime regime, possibly opening space for revisionist powers to contest routes that were previously secured (for example, Russia and China encountering less opposition on the routes of the Arctic and the Indo-Pacific, respectively). In summary, naval hegemony would fragment, and control of strategic seas would become contested, reconfiguring the relative influence of the USA, Russia, and maritime allies such as the United Kingdom and Japan.
Kjellén and the State as a Living Organism: Russian Expansion as an Organic Necessity
Another useful theoretical lens to interpret Russian geopolitical posture is that of Rudolf Kjellén, a Swedish political scientist of the early twentieth century who conceived the State as a living organism. Kjellén, who even coined the term “geopolitics,” was influenced by Friedrich Ratzel’s ideas and by social Darwinism, arguing that States are born, grow, and decline analogously to living beings [13]. In his work Staten som livsform (The State as a Form of Life, 1916), he maintained that States possess an organic dimension in addition to the legal one and that “just as any form of life, States must expand or die” [14]. This expansion would not be motivated merely by aggressive conquest but seen as a necessary growth for the self-preservation of the state organism [14]. In complement, Kjellén echoed Ratzel’s “law of expanding spaces” by asserting that large States expand at the expense of smaller ones, with it being only a matter of time before the great realms fill the available spaces [14]. That is, from the organic perspective, vigorous States tend to incorporate smaller neighboring territories, consolidating territorially much like an organism absorbing nutrients.
Applying this theory to the strategy of contemporary Russia, we can interpret Moscow’s actions—including the invasion of Ukraine and the ambition to restore its sphere of influence in Eurasia—as the expression of an organic drive for expansion. For a strategist influenced by this school, Russia (viewed as a state organism with a long imperial history) needs to expand its territory and influence to ensure its survival and security. The loss of control over spaces that once were part of the Russian Empire or the Soviet Union (such as Ukraine itself, the Caucasus, or Central Asia) may be perceived by Russian elites as an atrophy of the state organism, rendering it vulnerable. Thus, the reincorporation of these territories—whether directly (annexation) or indirectly (political vassalage)—would equate to restoring lost members or strengthening vital organs of the state body. In fact, official Russian arguments often portray Ukraine as an intrinsic part of “Russian historicity,” denying it a fully separate identity—a narrative that aligns with the idea that Russian expansion in that region is natural and necessary for the Russian State (seen as encompassing also Russian speakers beyond its current borders).
Kjellén would thus provide a theoretical justification for Russian territorial expansion as an organic phenomenon. As a great power, Russia would inevitably seek to expand at the expense of smaller neighbors (Ukraine, Georgia, the Baltic States, etc.), as dictated by the tendency of “great spaces to organize” to the detriment of the small [14]. This view can be identified in contemporary Russian doctrines that value spheres of influence and the notion that neighboring countries must gravitate around Moscow in order for the natural order to be maintained. The very idea of “Eurasia” united under Russian leadership (advocated by modern Russian thinkers) echoes this organic conception of vital space and expansion as a sign of the State’s vitality.
However, Kjellén’s theory also warns of the phenomenon of “imperial overstretch,” should a State exceed its internal cohesion limits by expanding excessively [14]. He recognized that extending borders too far could increase friction and vulnerabilities, making it difficult to maintain cohesion—a very large organism may lack functional integration. In the Russian context, this suggests that although expansion is seen as necessary, there are risks if Russia tries to encompass more than it can govern effectively. Conquering Ukraine and subjugating Eastern Europe, for example, could economically and militarily overburden the Russian State, especially if it faced resistance or had to manage hostile populations. However, in the hypothetical scenario we adopt (isolated USA and a weakened Europe), Russia might calculate that the organic benefits of expansion (territory, resources, strategic depth) would outweigh the costs, since external interference would be limited. Thus, through Kjellén’s lens, expansionist Russia behaves as an organism following its instinct for survival and growth, absorbing weaker neighbors; yet such a process is not devoid of challenges, requiring that the “organism Russia” manages to assimilate these new spaces without collapsing under its own weight.
Ratzel and Lebensraum: Resources, Territory, and the Justification for Expansion
Parallel to Kjellén’s organic view, Friedrich Ratzel’s theory offers another conceptual basis for understanding Russian expansion: the concept of Lebensraum (vital space). Ratzel, a German geographer of the late nineteenth century, proposed that the survival and development of a people or nation depended critically on the available physical space and resources. Influenced by Darwinist ideas, he applied the notion of “survival of the fittest” to nations, arguing that human societies need to conquer territory and resources to prosper, and that the stronger and fittest civilizations will naturally prevail over the weaker ones [12]. In 1901, Ratzel coined the term Lebensraum to describe this need for “vital space” as a geographical factor in national power [15].
Subsequently, this idea would be adopted—and extremely distorted—by Nazi ideology to justify Germany’s aggressions in Europe. However, the core of Ratzel’s concept is that territorial expansion is essential for the survival and growth of a State, especially to secure food, raw materials, and space for its population [12].
When examining Russia’s stance under this perspective, we can see several narratives that evoke the logic of Lebensraum. Russia is the largest country in the world by area; however, much of its territory is characterized by adverse climates (tundra, taiga) and is relatively sparsely populated in Siberia. On the other hand, adjacent regions such as Ukraine possess highly arable lands (chernozem—black soil), significant Slavic population density, and additional natural resources (coal in the Donbass, for example). An implicit justification for Russian expansion could be the search for supplementary resources and fertile lands to secure its self-sufficiency and power—exactly as Ratzel described that vigorous nations do. Historical records show that Ratzel emphasized agrarian primacy: he believed that new territories should be colonized by farmers, providing the food base for the nation [12]. Ukraine, historically called the “breadbasket of Europe,” fits perfectly into this vision of conquest for sustenance and agricultural wealth.
Furthermore, Ratzel viewed geography as a determinant of the destiny of nations—peoples adapted to certain habitats seek to expand them if they aspire to grow. In contemporary Russian discourse, there is often mention of the need to ensure security and territorial depth in the face of NATO, or to unite brotherly peoples (Russians and Russian speakers) within a single political space. Such arguments can be read as a modern translation of Lebensraum: the idea that the Russian nation, in order to be secure and flourish, must control a larger space, encompassing buffer zones and critical resources. This Russian “vital space” would naturally include Ukraine and other former Soviet republics, given the historical and infrastructural interdependence. Ratzel emphasized that peoples migrated and expanded when their original homeland no longer met their needs or aspirations [12]. Although contemporary Russia does not suffer from demographic pressure (on the contrary, it faces population decline), under the logic of a great power there is indeed a sentiment of geopolitical insufficiency for having lost influence over areas considered strategic. Thus, reconquering these areas would mean recovering the “habitat” necessary for the Russian nation to prosper and feel secure.
It is important to mention that, in Ratzel’s and Kjellén’s formulations, the pursuit of Lebensraum or organic expansion is not morally qualified—it is treated as a natural process in the politics of power. Thus, on the discursive level, Russia can avoid overly aggressive rhetoric and resort to “natural” justifications: for example, claiming that it needs to occupy Ukraine for defensive purposes (security space) or to reunify peoples (a common cultural and historical space). Beneath these justifications, however, resonates the geopolitical imperative to acquire more territory and resources as a guarantee of national survival, something consonant with Ratzel’s theory. In fact, Russian Realpolitik frequently prioritizes the control of energy resources (gas, oil) and transportation routes. Expanding its influence over central Eurasia would also mean controlling oil pipelines, gas lines, and logistical corridors—essential elements of modern Lebensraum understood as access to vital resources and infrastructure.
In summary, by conquering Ukraine and extending its reach into Eurasia, Russia could effectively invoke the concept of Lebensraum: presenting its expansion not as mere imperialism, but as a necessity to secure indispensable lands and resources for its people and to correct the “injustice” of a vital space diminished by post-Cold War territorial losses. The theories of Ratzel and Kjellén together paint a picture in which Russian expansion emerges almost as a natural law—the great State reclaiming space to ensure its survival and development at the expense of smaller neighbors.
Trump, NATO, and the Threat of American Withdrawal
One of the most alarming changes with Trump's return to power is the tense relationship with the North Atlantic Treaty Organization (NATO). Trump has long criticized allies for not meeting military spending targets, even threatening during his first term to withdraw the US from the alliance if members did not increase their contributions [2]. This threat, initially viewed with skepticism, became concrete after his re-election, leading European allies to seriously consider the possibility of having to defend themselves without American support [1]. In fact, Trump suggested in post-election interviews that the US would only remain in NATO if the allies “paid their bills” – otherwise, he “would seriously consider” leaving [2]. Such statements reinforced the warning that the US might not honor NATO's mutual defense commitment, precisely at a time of continuous Russian threat due to the war in Ukraine [1].
From a theoretical point of view, this posture of American retrenchment evokes the classic tension between maritime power and land power. Alfred Thayer Mahan emphasized that the global power of the US derived largely from its naval superiority and from alliances that ensured control over strategic maritime routes [9]. NATO, since 1949, has served not only to deter Soviet terrestrial advances in Eurasia, but also to secure the US naval presence in the North Atlantic and the Mediterranean – a fundamental element according to Mahan. In turn, Halford Mackinder warned that the balance of global power depended on the control of the Eurasian “Heartland” (the central region of Eurasia). The withdrawal or disengagement of the US (a maritime power) from this region could open the way for a continental power (such as Russia) to expand its influence in Eastern Europe, unbalancing the power balance [3]. In other words, by threatening to leave NATO, Trump jeopardizes the principle of containment that prevented Russian dominance over Eastern Europe – something that Mackinder would see as a dangerous shift in global power in favor of the Heartland power.
Adopting an impartial tone, it is observed that European countries have reacted to this new reality with precautionary measures. Strategic reports already calculate the cost of an autonomous European defense: hundreds of thousands of additional soldiers and investments of hundreds of billions of euros would be required if the US ceased to guarantee the security of the continent [1]. European dependence on American military power is significant and, without it, there would be a need for a major reinforcement of European Armed Forces [1]. This mobilization practically reflects the anticipation of a power vacuum left by the US – a scenario in which Mackinder’s theory (on the primacy of the Heartland and the vulnerability of the “external crescent” where Western Europe is located) regains its relevance.
The US–Ukraine Economic Agreement: Strategic Minerals in Exchange for Support?
Another novelty of Trump's second term is the unprecedented and transactional manner in which Washington has been dealing with the war in Ukraine. Instead of emphasizing security guarantees and alliances, the Trump administration proposed a trade agreement with Ukraine focused on the exploitation of strategic minerals, linking American support to a direct economic benefit. According to sources close to the negotiations, the US and Ukraine are about to sign a pact to share the revenues from the exploitation of critical mineral resources on Ukrainian territory [19]. Materials such as titanium, lithium, rare earths, and uranium – vital for high-tech and defense industries – would be at the core of this agreement [6]. According to the known draft, Ukraine would allocate 50% of the profits from new mineral ventures to a fund controlled by the US, which would reinvest part of the resources in the country’s own reconstruction [6] [19].
It is noteworthy that the pact does not include explicit security guarantees for Kyiv, despite Ukraine remaining under direct military threat from Russia [19]. Essentially, the Trump administration offers financial support and economic investment in exchange for a share in Ukrainian natural resources, but without formally committing to Ukraine's defense in the event of a renewed Russian offensive [19]. American authorities argue that this economic partnership would already be sufficient to “secure Ukrainian interests,” as it would provide the US with its own incentives to desire Ukraine’s stability [19]. “What could be better for Ukraine than being in an economic partnership with the United States?” stated Mike Waltz, a US national security advisor, defending the proposal [19].
Analysts, however, assess the agreement in divided terms. For some, it represents a form of economic exploitation at a time of Ukraine's fragility – comparing the demand to share mineral wealth amid war to a scheme of “mafia protection” [19]. Steven Cook, from the Council on Foreign Relations, classified the offer as “extortion,” and political scientist Virginia P. Fortna observed that charging resources from an invaded country resembles predatory practices [19]. Joseph Nye adds that it is a short-term gain strategy that could be “disastrous in the long run” for American credibility, reflecting the transactional approach that Trump even adopted with close allies in other contexts [19]. On the other hand, some see a future advantage for Kyiv: journalist Pierre Briançon suggests that at least this agreement aligns American commercial interests with Ukraine’s future, which could, in theory, keep the US involved in Ukrainian prosperity in the long term [19]. It is even recalled that President Zelensky himself proposed last year the idea of sharing natural resources with the US to bring the interests of the two countries closer together [19].
From the perspective of geopolitical theories, this agreement illustrates a shift towards economic pragmatism in international relations, approaching concepts proposed by Kjellén. Rudolf Kjellén, who coined the term “geopolitics,” saw the State as a territorial organism that seeks to ensure its survival through self-sufficiency and the control of strategic resources [4]. Trump's demand for a share in Ukrainian resources in order to continue supporting the country reflects a logic of autarky and direct national interest – that is, foreign policy serving primarily to reinforce the economic and material position of the US. This view contrasts with the traditional cooperative approach, but aligns with Kjellén’s idea that powerful States tend to transform international relations into opportunities for their own gain, ensuring access to vital raw materials. Similarly, Friedrich Ratzel argued that States have a “propensity to expand their borders according to their capacities,” seeking vital space (Lebensraum) and resources to sustain their development [11]. The US–Ukraine pact, by conditioning military/economic aid on obtaining tangible advantages (half of the mineral profits), is reminiscent of Ratzel’s perspective: the US, as a rising economic power, expands its economic influence over Ukrainian territory like an organism extending itself to obtain the necessary resources for its well-being. It is, therefore, a form of economic expansionism at the expense of purely ideological commitments or collective security.
Peace Negotiations Excluding Ukraine and the Legitimacy of the Agreement
Another controversial point is the manner in which peace negotiations between Russia and the West have been conducted under Trump's administration. Since taking office, the American president has engaged directly with Moscow in pursuit of a ceasefire, deliberately keeping the Ukrainian government out of the initial discussions [6]. Trump expressed his desire to “leave Zelensky out of the conversation” and also excluded the European Union from any influence in the process [6]. This negotiation strategy—conducted without the presence of the primary interested party, Ukraine—raises serious questions about the legitimacy and sustainability of any resulting agreement.
Historically, peace agreements reached without the direct participation of one of the conflicting parties tend to face problems in implementation and acceptance.
The exclusion of Ukraine in the decision-making phase brings to light the issue of guarantees. As noted, the emerging agreement lacks formal US security guarantees for Ukraine. This implies that, after the agreement is signed, nothing will prevent Russia from launching a new offensive if it deems it convenient, knowing that the US has not committed to defending it militarily. Experts have already warned that a ceasefire without robust protection may only be a pause for Russian rearmament, rendering the conflict “frozen” temporarily and potentially resumed in the near future. The European strategic community has expressed similar concern: without American deterrence, the risk of further Russian aggressions in the region increases considerably [1]. Denmark, for example, has released intelligence reports warning of possible imminent Russian attacks, prompting neighboring countries to accelerate plans for independent defense [1].
The legitimacy of this asymmetric peace agreement (negotiated without Ukraine fully at the table and under economic coercion) is also questionable from a legal and moral point of view. It violates the principle of self-determination by imposing terms decided by great powers on a sovereign country—a practice reminiscent of dark chapters in diplomacy, such as the Munich Agreement of 1938, when powers determined the fate of Czechoslovakia without its consent. In the current case, Ukraine would end up signing the agreement, but from a position of weakness, raising doubts about how durable such a commitment would be.
From Mackinder’s perspective, Ukraine’s removal from the battlefield without guarantees essentially means admitting a greater influence of Russia (the Heartland power) over Eastern Europe. This would alter the balance in Eurasia in a potentially lasting way. Furthermore, the fact that great powers negotiate over the heads of a smaller country evokes the imperial logic of the nineteenth and early twentieth centuries, when empires decided among themselves the divisions of foreign territories—a behavior that Mackinder saw as likely in a world of a “closed system.” With the entire world already occupied by States, Mackinder predicted that powers would begin to compete for influence within this consolidated board, often subjugating smaller states to gain advantage [3]. The US–Russia negotiation regarding Ukraine, without proper Ukrainian representation, exemplifies this type of neo-imperial dynamic in the twenty-first century.
Also noteworthy is the consonance with the ideas of Ratzel and Kjellén: both viewed smaller states as easily relegated to the status of satellites or even “parasitic organisms” in the orbit of larger states. Kjellén spoke of the intrinsic vulnerability of states with little territorial depth or economic dependence, making them susceptible to external pressures [4][20]. Ukraine, weakened by war and dependent on external aid, becomes a concrete example of this theorized vulnerability: it has had to cede strategic resources and accept terms dictated against its will in an attempt to secure its immediate survival. The resulting agreement, therefore, reflects a power imbalance characteristic of the hierarchical international relations described by classical geopolitical theorists.
Implicit Territorial Concessions and Trump’s Public Discourse
A central and controversial point in Trump’s statements regarding the war in Ukraine is the insinuation of territorial concessions to Russia as part of the conflict’s resolution. Publicly, Trump avoided explicitly condemning Russian aggression and even stated that he considered it “unlikely” that Ukraine would be able to retake all the areas occupied by the Russians [16]. In debates and interviews, he suggested that “if I were president, the war would end in 24 hours,” implying that he would force an understanding between Kyiv and Moscow that would likely involve ceding some territory in exchange for peace. This position marks a break with the previous US policy of not recognizing any territorial acquisitions made by force and fuels speculations that a future peace agreement sponsored by Trump would legitimize at least part of Russia’s gains since 2014 (Crimea, Donbass, and areas seized during the 2022 invasion).
The actions of his administration corroborate this interpretation. As discussed, the economic agreement focuses on the exploitation of Ukrainian natural resources, many of which are located precisely in regions currently under Russian military control, such as parts of the Zaporizhzhia Oblast, Donetsk, Lugansk, and the Azov Sea area [6]. A Ukrainian geologist, Hanna Liventseva, highlighted that “most of these elements (strategic minerals) are found in the south of the Ukrainian Shield, mainly in the Azov region, and most of these territories are currently invaded by Russia” [6]. This means that, to make joint exploitation viable, Russia’s de facto control over these areas would have to be recognized—or at least tolerated—in the short term. In other words, the pact indirectly and tacitly accepts Russian territorial gains, as it involves sharing the profits from resources that are not currently accessible to the Kyiv government.
Furthermore, figures close to Trump have made explicit statements regarding the possibility of territorial cession. Mike Waltz, Trump’s national security advisor, publicly stated that Zelensky might need to “cede land to Russia” to end the war [8]. This remark—made public in March 2025—confirms that the Trump White House considers it natural for Ukraine to relinquish parts of its territory in favor of an agreement. Such a stance marks a break from the previous Western consensus, which condemned any territorial gains by force. Under Trump, a pragmatic view (in the eyes of his supporters) or a cynical one (according to his critics) seems to prevail: sacrificing principles of territorial integrity to quickly end hostilities and secure immediate economic benefits.
In theoretical terms, this inclination to validate territorial gains by force recalls the concept of Realpolitik and the geopolitical Darwinism that influenced thinkers such as Ratzel. In Ratzel’s organic conception, expanding states naturally absorb neighboring territories when they are strong enough to do so, while declining states lose territory—a process almost biological in the selection of the fittest [11]. The Trump administration’s acceptance that Ukraine should “give something” to Moscow to seal peace reflects a normalization of this geopolitical selection process: it recognizes the aggressor (Russia) as having the “right” to retain conquered lands, because that is how power realities on the ground dictate. Mackinder, although firmly opposed to allowing Russia to dominate the Heartland, would see this outcome as the logical consequence of the lack of engagement from maritime powers (the USA and the United Kingdom, for example) in sustaining the Ukrainian counterattack. Without the active involvement of maritime power to balance the dispute, land power prevails in Eastern Europe.
From the perspective of international legitimacy, the cession of Ukrainian territories—whether de jure or de facto—creates a dangerous precedent in the post-Cold War era. Rewarding violent aggression with territorial gains may encourage similar strategies in other parts of the world, undermining the architecture of collective security. This is possibly a return to a world of spheres of influence, where great powers define borders and zones of control according to their convenience—something that the rules-based order after 1945 sought to avoid. Here, academic impartiality requires noting that coercion for territorial concessions rarely produces lasting peace, as the aggrieved party—in this case, Ukraine—may accept temporarily but will continue to assert its rights in the long term, as has occurred with other territorial injustices in history.
Territorial Ambitions of Trump: Greenland and Canada
Beyond the Eurasian theater of war, Trump revived geopolitical ambitions involving territories traditionally allied with the US: Greenland (an autonomous territory of Denmark) and Canada. As early as 2019, during his first term, Trump shocked the world by proposing to buy Greenland—rich in minerals and strategically positioned in the Arctic. Upon his return to power, he went further: expressing a “renewed interest” in acquiring Greenland and publicly suggesting the incorporation of Canada as the 51st American state [2].
In January 2025, during a press conference at Mar-a-Lago, he even displayed maps in which the US and Canada appeared merged into a single country, while Greenland was marked as a future American possession [2]. Posts by the president on social media included satirical images with a map of North America where Canada was labeled “51st” and Greenland designated as “Our Land” [2].
Such moves were met with concern and disbelief by allies. Canadian Prime Minister Justin Trudeau was caught on an open microphone warning that Trump’s fixation on annexation “is real” and not just a joke [7]. Trudeau emphasized that Washington appeared to covet Canada’s vast mineral resources, which would explain the insistence on the idea of absorption [7]. In public, Trump argued that Canadians “would be more prosperous as American citizens,” promising tax cuts and better services should they become part of the US [7]. On the Danish side, the reaction to the revived plan regarding Greenland was firmly negative—as it was in 2019—reaffirming that the territory is not for sale. Trump, however, insinuated that the issue might be one of national security, indicating that American possession of Greenland would prevent adverse influences (a reference to China and Russia in the Arctic) [2]. More worryingly, he refused to rule out the use of military means to obtain the island, although he assured that he had no intention of invading Canada by force (in the Canadian case, he spoke of “economic force” to forge a union) [2].
This series of initiatives reflects an unprecedented expansionist impetus by the US in recent times, at least in discourse. Analyzing this through the lens of classical geopolitics offers interesting insights. Friedrich Ratzel and his notion of Lebensraum suggest that powerful states, upon reaching a certain predominance, seek to expand their territory by influencing or incorporating adjacent areas. Trump, by targeting the immediate neighbor (Canada) and a nearby strategic territory (Greenland), appears to resurrect this logic of territorial expansion for the sake of gaining space and resources. Ratzel saw such expansion almost as a natural process for vigorous states, comparable to the growth of an organism [11]. From this perspective, the US would be exercising its “right” of expansion in North America and the polar region, integrating areas of vital interest.
Additionally, Alfred Mahan’s view on maritime power helps to understand the strategic value of Greenland. Mahan postulated that control of key maritime chokepoints and naval bases ensures global advantage [9]. Greenland, situated between the North Atlantic and the Arctic, has become increasingly relevant as climate change opens new polar maritime routes and reveals vast mineral deposits (including rare earth elements and oil). For the US, having a presence or sovereignty over Greenland would mean dominating the gateway to the Arctic and denying this space to rivals. This aligns with Mahan’s strategy of securing commercial and military routes (in this case, potential Arctic routes) and resources to consolidate naval supremacy. On the other hand, the incorporation of Canada—with its enormous territory, Arctic coastline, and abundant natural resources—would provide the US with formidable geoeconomic and geopolitical reinforcement, practically eliminating vulnerabilities along its northern border. This is an ambitious project that also echoes ideas of Kjellén, for whom an ideal State should seek territorial completeness and economic self-sufficiency within its region. Incorporating Canada would be the pinnacle of American regional autarky, turning North America into a unified bloc under Washington (a scenario reminiscent of the “pan-regions” conceived by twentieth-century geopoliticians influenced by Kjellén).
It is important to note, however, that these ambitions face enormous legal and political obstacles. The sovereignty of Canada and Greenland (Denmark) is guaranteed by international law, and both peoples categorically reject the idea of annexation. Any hostile action by the US against these countries would shake alliances and the world order itself. Even so, the very fact that an American president suggests such possibilities already produces geopolitical effects: traditional partners begin to distrust Washington’s intentions, seek alternative alliances, and strengthen nationalist discourses of resistance. In summary, Trump’s expansionist intentions in Greenland and Canada rekindle old territorial issues and paradoxically place the US in the position of a revisionist power—a role once associated with empires in search of colonies.
Implications for Brazil and South America: A New Neocolonization?
In light of this geopolitical reconfiguration driven by Trump's USA—with a reordering of alliances and a possible partition of spheres of influence among great powers—the question arises: what is the impact on Brazil and the other countries of South America? Traditionally, Latin America has been under the aegis of the Monroe Doctrine (1823), which established non-interference by Europe in the region and, implicitly, the primacy of the USA in the Western Hemisphere. In the post–Cold War period, this influence translated more into political and economic leadership, without formal annexations or direct territorial domination. However, the current context points to a kind of “neocolonization” of the Global South, in which larger powers seek to control resources and peripheral governments in an indirect yet effective manner.
Mackinder’s theories can be used to illuminate this dynamic. As mentioned, Mackinder envisioned the twentieth-century world as a closed system, in which there were no longer any unknown lands to be colonized—hence, the powers would fight among themselves for control over already occupied regions [3]. He predicted that Africa and Latin America (then largely European colonies or semi-colonies) would continue as boards upon which the great powers would project their disputes, a form of neocolonialism. In the current scenario, we see the USA proposing exchanges of protection for resources (as in Ukraine) and even leaders of developing countries seeking similar agreements. A notable example: the President of the Democratic Republic of the Congo, Felix Tshisekedi, praised the USA–Ukraine initiative and suggested an analogous agreement involving Congolese mineral wealth in exchange for US support against internal rebels (M23) [19]. In other words, African countries and possibly South American ones may enter into this logic of offering privileged access to resources (cobalt, lithium, food, biodiversity) in order to obtain security guarantees or investments. This represents a regression to the times when external powers dictated the directions of the South in exchange for promises of protection, characterizing a strategic neocolonialism.
For Brazil, in particular, this rearrangement generates both opportunities and risks. As a regional power with considerable diplomatic autonomy, Brazil has historically sought to balance relationships with the USA, Europe, China, and other actors, avoiding automatic alignments. However, in a world where Trump’s USA is actively redefining spheres of influence—possibly making deals with Russia that divide priorities (for example, Washington focusing on the Western Hemisphere and Moscow on the Eastern)—South America could once again be seen as an exclusive American sphere of influence. From this perspective, Washington could pressure South American countries to align with its directives, limiting partnerships with rivals (such as China) and seeking privileged access to strategic resources (such as the Amazon, fresh water, minerals, and agricultural commodities). Some indications are already emerging: Trump’s transactional approach mentioned by Nye included pressures on Canada and Mexico regarding border and trade issues, under the threat of commercial sanctions. It would not be unthinkable to adopt a hard line, for example, with regard to Brazilian environmental policies (linked to the Amazon) or Brazil’s relations with China, using tariffs or incentives as leverage—a sort of geopolitics of economic coercion.
On the other hand, Brazil and its neighbors could also attempt to take advantage of the Sino–North American competition. If the USA is distracted consolidating its hemispheric “hard power” hegemony (even with annexation fantasies in the north), powers such as China may advance their economic presence in South America through investments and trade (Belt and Road, infrastructure financing)—which is already happening. This would constitute an indirect neocolonial dispute in the South: Chinese loans and investments versus American demands and agreements, partly reminiscent of the nineteenth-century imperial competition (when the United Kingdom, USA, and others competed for Latin American markets and resources).
From a conceptual standpoint, Mackinder might classify South America as part of the “Outer Crescent” (external insular crescent)—peripheral to the great Eurasian “World-Island,” yet still crucial as a source of resources and a strategic position in the South Atlantic and Pacific. If the USA consolidates an informal empire in the Americas, it would be reinforcing its “insular bastion” far from the Eurasian Heartland, a strategy that Mackinder once suggested for maritime powers: to control islands and peripheral continents to compensate for the disadvantage of not controlling the Heartland. However, an excessive US dominance in the South could lead to local resistance and alternative alignments, unbalancing the region.
Kjellén would add that for Brazil to maintain its decisive sovereignty, it will need to strengthen its autarky and internal cohesion—in other words, reduce vulnerabilities (economic, military, social) that external powers might exploit [4]. Meanwhile, Mahan might point out the importance for Brazil of controlling its maritime routes and coastlines (South Atlantic) to avoid being at the mercy of a naval power like the USA. And Ratzel would remind us that states that do not expand their influence tend to be absorbed by foreign influences—which, in the context of Brazil, does not mean conquering neighboring territories, but rather actively leading South American integration to create a block more resilient to external intrusion.
In summary, South America finds itself in a more competitive and segmented world, where major players are resurrecting practices from past eras. The notion of “neocolonization” here does not imply direct occupation, but rather mechanisms of dependency: whether through unequal economic agreements or through diplomatic or military pressure for alignment. Brazil, as the largest economy and territory on the subcontinent, will have to navigate with heightened caution. A new global power balance, marked by the division of spheres of influence among the USA, China, and Russia, may reduce the sovereign maneuvering space of South American countries unless they act jointly. Thus, theoretical reflection suggests the need for South–South strategies, reinforcement of regional organizations, and diversification of partnerships to avoid falling into modern “neocolonial traps.”
Conclusion
The emerging post–re-election geopolitical conjuncture of Donald Trump signals a return to classical geopolitical principles, after several decades of predominance of institutional liberal views. We witness the revaluation of concepts such as spheres of influence, exchanges of protection for resources, naval power versus land power, and disputes over territory and raw materials—all central themes in the writings of Mackinder, Mahan, Kjellén, and Ratzel at the end of the nineteenth and the beginning of the twentieth century. An impartial analysis of these events, in light of these theories, shows internal coherence in Trump’s actions: although controversial, they follow a logic of maximizing national interest and the relative power of the USA on the world stage, even at the expense of established principles and alliances.
Halford Mackinder reminds us that, in a closed world with no new lands to conquer, the great powers will seek to redistribute the world among themselves [3]. This seems to manifest in the direct understandings between the USA and Russia over the fate of Ukraine, and in American ambitions in the Arctic and the Western Hemisphere. Alfred Mahan emphasizes that the control of the seas and strategic positions ensures supremacy—we see reflections of this in Trump’s obsession with Greenland (Arctic) and the possible neglect of the importance of maintaining NATO (and therefore the North Atlantic) as a cohesive bloc, something that Mahan’s theory would criticize due to the risk of a naval vacuum. Rudolf Kjellén and Friedrich Ratzel provide the framework to understand the more aggressive facet of expansionist nationalism: the idea of the State as an organism that needs to grow, secure resources, and seek self-sufficiency explains everything from the extortionate agreement imposed on Ukraine to the annexation rhetoric regarding Canada.
The potential consequences are profound. In the short term, we may witness a precarious ceasefire in the Ukraine war, with consolidated Russian territorial gains and Ukraine economically tied to the USA, but without formal military protection—a fragile “armed peace.” Western Europe, alarmed, may accelerate its independent militarization, perhaps marking the beginning of European defense autonomy, as is already openly debated [1]. At the far end of the globe, American activism in the Arctic and the Americas may reshape alliances: countries like Canada, once aligned with Washington, might seek to guarantee their sovereignty by distancing themselves from it; powers like China could take advantage of the openings to increase their presence in Latin America and Africa through economic diplomacy; and emerging countries of the Global South may have to choose between submitting to new “guardianships” or strengthening South–South cooperation.
Ultimately, the current situation reinforces the relevance of studying geopolitics through historical lenses. The actions of the Trump administration indicate that, despite all technological and normative advances, the competition for geographic power has not disappeared—it has merely assumed new formats. Academic impartiality obliges us not to prematurely judge whether these strategies will be successful or beneficial, but history and theory warn that neo-imperial movements tend to generate counter-reactions. As Mackinder insinuated, “every shock or change anywhere reverberates around the world,” and a sudden move by a superpower tends to provoke unforeseen adjustments and chain conflicts. It remains to be seen how the other actors—including Brazil and its neighbors—will adapt to this new chapter in the great struggle for global power, in which centuries-old theories once again have a surprising explanatory power over present events.
Bibliography
[1] A Referência. (2025). Europa calcula o custo de se defender sem os EUA: 300 mil soldados e 250 bilhões de euros a mais. Recuperado em 3 de março de 2025, de https://areferencia.com/europa/europa-calcula-o-custo-de-se-defender-sem-os-eua-300-mil-soldados-e-250-bilhoes-de-euros-a-mais/#:\~:text=Europa%20calcula%20o%20custo%20de,bilh%C3%B5es%20de%20euros%20a%20mais
[2] Brexit Institute. (2025). What happens if Trump invades Greenland? Recuperado em 3 de março de 2025, de https://dcubrexitinstitute.eu/2025/01/what-happens-if-trump-invades-greenland/#:\~:text=Ever%20since%20Donald%20Trump%20announced,agreed%20in%20Wales%20in%202014
[3] Cfettweis C:CST22(2)8576.DVI. (2025). Mackinder and Angell. Recuperado em 3 de março de 2025, de https://cfettweis.com/wp-content/uploads/Mackinder-and-Angell.pdf#:\~:text=meant%20the%20beginning%20of%20an,Mackinder
[4] Diva-Portal. (2025). The geopolitics of territorial relativity. Poland seen by Rudolf Kjellén. Recuperado em 3 de março de 2025, de https://www.diva-portal.org/smash/get/diva2:1696547/FULLTEXT02#:\~:text=,The%20state%20territory
[5] Geopolitical Monitor. (2025). The Russo-Ukrainian War and Mackinder’s Heartland Thesis. Recuperado em 3 de março de 2025, de https://www.geopoliticalmonitor.com/the-ukraine-war-and-mackinders-heartland-thesis/#:\~:text=In%201904%2C%20Sir%20Halford%20J,in%20adding%20a%20substantial%20oceanic
[6] Instituto Humanitas Unisinos. (2025). Trump obriga Zelensky a hipotecar a exploração de minerais críticos em troca do seu apoio. Recuperado em 3 de março de 2025, de https://www.ihu.unisinos.br/648986-trump-obriga-zelensky-a-hipotecar-a-exploracao-de-minerais-criticos-em-troca-do-seu-apoio#:\~:text=Essa%20troca%20inclui%20os%20cobi%C3%A7ados,s%C3%A3o%20praticamente%20inexploradas%20no%20pa%C3%ADs
[7] Politico. (2025). Trump’s annexation fixation is no joke, Trudeau warns. Recuperado em 3 de março de 2025, de https://www.politico.com/news/2025/02/07/canada-trudeau-trump-51-state-00203156#:\~:text=TORONTO%20%E2%80%94%20Prime%20Minister%20Justin,Canada%20becoming%20the%2051st%20state%2C%E2%80%9D%20Trudeau%20said
[8] The Daily Beast. (2025). Top Trump Adviser Moves Goalpost for Ukraine to End War. Recuperado em 3 de março de 2025, de https://www.thedailybeast.com/top-trump-adviser-moves-goalpost-for-ukraine-to-end-war/#:\~:text=LAND%20GRAB
[9] The Geostrata. (2025). Alfred Thayer Mahan and Supremacy of Naval Power. Recuperado em 3 de março de 2025, de https://www.thegeostrata.com/post/alfred-thayer-mahan-and-supremacy-of-naval-power#:\~:text=Alfred%20Thayer%20Mahan%20and%20Supremacy,control%20over%20maritime%20trade%20routes
[10] U.S. Department of State. (2025). Mahan’s The Influence of Sea Power upon History: Securing International Markets in the 1890s. Recuperado em 3 de março de 2025, de https://history.state.gov/milestones/1866-1898/mahan#:\~:text=Mahan%20argued%20that%20British%20control,American%20politicians%20believed%20that%20these
[11] Britannica. (2025a). Friedrich Ratzel | Biogeography, Anthropogeography, Political Geography. Recuperado em 3 de março de 2025, de https://www.britannica.com/biography/Friedrich-Ratzel#:\~:text=webster,Swedish%20political%20scientist%20%2076
[12] Britannica. (2025b). Lebensraum. Recuperado em 3 de março de 2025, de https://www.britannica.com/topic/Lebensraum#:\~:text=defined,The
[13] Britannica. (2025c). Rudolf Kjellén. Recuperado em 3 de março de 2025, de https://www.britannica.com/biography/Rudolf-Kjellen
[14] Wikipedia (ZH). (2025). Rudolf Kjellén. Recuperado em 3 de março de 2025, de https://zh.wikipedia.org/wiki/w:Rudolf_Kjell%C3%A9n#:\~:text=Besides%20legalistic%2C%20states%20have%20organic,preservation.%20%5B%203
[15] Wikipedia. (2025). Lebensraum. Recuperado em 3 de março de 2025, de https://en.wikipedia.org/wiki/Lebensraum#:\~:text=The%20German%20geographer%20and%20ethnographer,into%20the%20Greater%20Germanic%20Reich
[16] YouTube. (2025). Trump says Ukraine 'unlikely to get all land back' or join NATO [Vídeo]. Recuperado em 3 de março de 2025, de https://www.youtube.com/watch?v=BmHzAVLhsXU#:\~:text=Trump%20says%20Ukraine%20%27unlikely%20to,for%20it%20to%20join%20NATO
[17] U.S. Naval Institute. (2025) Operation World Peace. Recuperado em 3 de março de 2025, de https://www.usni.org/magazines/proceedings/1955/june/operation-world-peace#:\\~:text=“The Mahan doctrine%2C” according to,the word “airships” is more
[18] Emissary. (2024) Trump’s Greenland and Panama Canal Threats Are a Throwback to an Old, Misguided Foreign Policy. Recuperado em 3 de março de 2025, de https://carnegieendowment.org/emissary/2025/01/trump-greenland-panama-canal-monroe-doctrine-policy?lang=en
[19] A Referência. Acordo EUA-Ucrânia está praticamente fechado, mas analistas se dividem sobre quem sairá ganhando. Recuperado em 3 de março de 2025, de https://areferencia.com/europa/acordo-eua-ucrania-esta-praticamente-fechado-mas-analistas-se-dividem-sobre-quem-saira-ganhando/#:\\~:text=EUA e 17,o acordo a seu favor
[20] Wikipedia. (2025) Geopolitik. Recuperado em 3 de março de 2025, de https://en.wikipedia.org/wiki/Geopolitik#:\\~:text=Rudolph Kjellén was Ratzel's Swedish,Kjellén's State
-
 @ 5d4b6c8d:8a1c1ee3
2025-03-07 14:30:14
@ 5d4b6c8d:8a1c1ee3
2025-03-07 14:30:14Somehow, the NFL just keeps being in the news. - A bunch of big name players have either been cut already or will certainly be cut and some others have made trade requests. - How did the combine shake up the draft picture? - The combination of depth and high-end talent at certain positions makes draft strategy interesting this year.
The NBA season is chugging along towards the finish line. - How are people watching NBA? I cancelled YouTubeTV after the Super Bowl and I hate League Pass. Are there better options? - The MVP race might be a done deal - The Raptors stink, but @grayruby holds out hope - For some reason Bam is of interest, despite the Heat being about as mid as a team can be
In other news, - We've got some contest updates for the territory - Ovi is closing in on the scoring record (Lebron getting to 50k points probably deserves a mention, too). Is it the era of old athletes or have we just gotten lucky with a few. - NHL trade deadline today: who got moved and did it matter? - Something about MLB teams playing in minor league parks: Why? - Lots of active sports markets at Predyx
Plus, anything the stackers want us to cover.
originally posted at https://stacker.news/items/906502
-
 @ 147ac18e:ef1ca1ba
2025-03-07 14:04:46
@ 147ac18e:ef1ca1ba
2025-03-07 14:04:46The world is on the brink of a technological shift, where artificial intelligence (AI) is becoming increasingly autonomous. With AI agents conducting transactions, hiring other AI agents, and managing digital assets, a critical question arises: What form of money will power this new AI-driven economy? The answer, as some industry experts predict, is Bitcoin.
The Rise of the Autonomous Economy
AI agents are no longer just tools executing predefined tasks; they are evolving into independent economic actors capable of initiating transactions, negotiating terms, and paying for services. The transaction volume within AI-driven economies is projected to be 100 times larger than human transactions, as each person may have dozens or even hundreds of AI agents working on their behalf. This creates an unprecedented demand for a seamless, efficient, and universally accepted form of digital money.
Why Bitcoin is the Natural Choice for AI Transactions
Bitcoin stands out as the ideal currency for AI-driven economies for several reasons:
-
Borderless and Permissionless: Unlike traditional banking systems that require identity verification (KYC/AML) and impose restrictions based on geography, Bitcoin allows AI agents to transact freely without human intervention.
-
Personless Transactions: AI agents, by nature, do not have legal identities, making it impossible for them to interact with banks or obtain credit cards. Bitcoin provides a neutral medium that does not require a legal entity to use it.
-
Energy-Backed Economy: AI agents function on computational power, which is an energy-intensive process. Bitcoin’s proof-of-work mechanism aligns well with this model, as it is also backed by computational energy. AI systems will inherently recognize Bitcoin as a valid medium of exchange due to this energy linkage.
-
Micropayments via Lightning Network: AI transactions will often involve micropayments—small fees for data processing, information retrieval, and digital labor. Traditional financial networks are inefficient in handling such transactions due to high fees and processing delays. The Bitcoin Lightning Network enables instant, low-cost micropayments, making it perfect for AI-to-AI financial interactions.
-
Immutability and Transparency: AI systems require trustless environments where transaction history cannot be altered or reversed. Bitcoin’s blockchain ensures that all transactions are transparent and immutable, reducing fraud and enabling verifiable AI-driven commerce.
The Symbiotic Growth of Bitcoin and AI
As AI-driven economies expand, Bitcoin adoption will accelerate in the following ways:
-
Increased Transaction Volume: With billions of AI transactions occurring daily, Bitcoin will see an explosion in on-chain and Lightning Network activity, solidifying its position as the world’s primary digital currency.
-
Institutional and Enterprise Adoption: As businesses integrate AI into their workflows, they will increasingly adopt Bitcoin to facilitate machine-to-machine payments, smart contracts, and decentralized finance (DeFi) solutions.
-
Regulatory Shift Towards Decentralized Currencies: Governments and financial institutions will have to acknowledge Bitcoin’s role in AI economies and adjust regulatory frameworks accordingly, further legitimizing its use.
-
Bitcoin as a Store of Value for AI: AI systems will not only use Bitcoin for transactions but may also accumulate it as a reserve asset due to its deflationary nature and finite supply.
The Future: Bitcoin as the De Facto AI Currency
As AI continues to reshape industries, Bitcoin is poised to become the backbone of an autonomous digital economy. The fusion of AI and Bitcoin will create a self-sustaining loop where AI agents fuel Bitcoin’s transactional utility, and Bitcoin’s decentralized nature enables AI’s economic autonomy. This symbiosis will not only drive Bitcoin adoption but could also redefine global economic structures.
In this AI-driven future, Bitcoin may not just be a currency for humans—it could very well be the native currency of artificial intelligence.
Episode link: https://fountain.fm/episode/Ds1qicPmbC3udErQ7J3z
-
-
 @ a012dc82:6458a70d
2025-03-07 13:17:07
@ a012dc82:6458a70d
2025-03-07 13:17:07In an era where digital currencies are becoming as commonplace as traditional banking, a groundbreaking development has emerged from the UK, capturing the attention of both financial experts and law enforcement agencies worldwide. The UK police have made a monumental discovery, uncovering a staggering $1.7 billion in Bitcoin, intricately linked to a vast investment fraud scheme with roots deep in China. This revelation not only highlights the growing issue of cybercrime and financial fraud but also showcases the sophisticated methods employed by criminals to exploit the digital currency landscape for illicit purposes.
Table of Contents
-
The Discovery
-
The Accusation
-
The Implications
-
The Investigation
-
The Broader Impact
-
Conclusion
-
FAQs
The Discovery
The astonishing discovery was made amidst the trial of Jian Wen, a 42-year-old UK citizen embroiled in allegations of money laundering connected to a massive $6 billion investment fraud scheme. This scheme, masterminded by Zhimin Qian, known to some as Yadi Zhang, has left approximately 130,000 investors in China in dire straits, their investments vanished into the ether. The UK police's breakthrough in tracing the Bitcoin linked to this scheme underscores the meticulous and technologically advanced tactics utilized by law enforcement to combat digital financial crimes. The ability to trace such a significant amount of Bitcoin back to a specific fraud case marks a significant achievement in the realm of financial crime investigation, reflecting the increasing capability of global law enforcement agencies to adapt to the challenges posed by the digital age.
The Accusation
Jian Wen finds herself at the center of this complex web of financial deceit, accused of attempting to launder the ill-gotten gains from the fraudulent scheme. Her alleged attempts to funnel these vast sums into the London real estate market, though ultimately unsuccessful, paint a vivid picture of the lengths to which individuals involved in such schemes will go to legitimize their criminal proceeds. Wen's steadfast denial of the allegations against her adds a layer of intrigue to the case, challenging prosecutors to untangle the sophisticated methods used to disguise the fraudulent origins of the funds. This case highlights the critical need for vigilance and sophistication in tracking financial transactions across the globe, as criminals increasingly turn to complex schemes and digital currencies to obscure their activities.
The Implications
The implications of this case extend far beyond the immediate legal battle unfolding in London. It shines a spotlight on the dark underbelly of the digital currency world, where anonymity and the lack of regulatory oversight can too easily be exploited for nefarious purposes. The use of Bitcoin and other cryptocurrencies in money laundering and fraud schemes poses significant challenges for regulators and law enforcement worldwide. This case serves as a stark reminder of the urgent need for international cooperation and regulatory harmonization to address the vulnerabilities of the digital financial system. As cryptocurrencies continue to gain mainstream acceptance, the need for enhanced regulatory frameworks and advanced technological tools to monitor and control digital financial transactions becomes increasingly apparent.
The Investigation
The investigation leading to the discovery of the $1.7 billion in Bitcoin is a testament to the evolving landscape of law enforcement in the digital age. The success of the UK police in tracing these funds highlights the advancements in forensic technology and the growing expertise within law enforcement agencies in navigating the complex world of cryptocurrency transactions. This case exemplifies the potential for collaboration between financial institutions, regulatory bodies, and international law enforcement agencies to combat financial crime effectively. The ability to trace and recover assets in cryptocurrency form represents a significant step forward in the global fight against money laundering and investment fraud, setting a precedent for future investigations.
The Broader Impact
The uncovering of this vast sum of Bitcoin linked to the China fraud scheme has far-reaching implications for the cryptocurrency market and the broader financial ecosystem. It raises critical questions about the security and stability of digital currencies and the potential for their misuse in criminal enterprises. This case could serve as a catalyst for change, prompting policymakers and regulators to implement more stringent controls on cryptocurrency transactions and enhance the transparency of digital financial systems. As the digital currency market continues to evolve, the lessons learned from this investigation will undoubtedly influence the development of policies and technologies designed to protect investors and maintain the integrity of the financial system.
Conclusion
The discovery of $1.7 billion in Bitcoin by the UK police marks a watershed moment in the fight against international financial fraud. As the trial against Jian Wen progresses, it promises to offer unprecedented insights into the mechanisms of cryptocurrency laundering and the global nature of financial crime. This case not only underscores the critical role of digital currencies in the modern financial landscape but also highlights the imperative for continuous vigilance, innovation, and cooperation among law enforcement, regulatory bodies, and the financial industry at large. In the quest to safeguard the integrity of the global financial market, the unraveling of this $1.7 billion Bitcoin mystery represents both a significant challenge and a vital opportunity for the future of financial security and crime prevention.
FAQs
Who is Jian Wen, and what are the accusations against her? Jian Wen is a 42-year-old UK citizen accused of attempting to launder the proceeds of a $6 billion investment fraud scheme from China by investing in high-value properties in London. She denies the allegations.
How did the UK police trace the Bitcoin linked to the fraud? The UK police utilized advanced forensic technology and collaborated with international law enforcement agencies to trace the Bitcoin transactions back to the fraud scheme, demonstrating their growing expertise in combating digital financial crimes.
What are the broader implications of this case for the cryptocurrency market? This case highlights the potential for misuse of cryptocurrencies in money laundering and fraud schemes, raising questions about the need for enhanced regulatory frameworks and technological tools to monitor digital financial transactions.
What does this case reveal about the challenges of combating financial crime in the digital age? The case underscores the complexities and challenges law enforcement faces in tracking and prosecuting financial crimes that exploit digital currencies, emphasizing the need for international cooperation and advanced technological capabilities.
How might this discovery influence future regulatory policies on cryptocurrencies? The discovery could prompt policymakers and regulators to implement stricter controls on cryptocurrency transactions and develop more transparent and secure digital financial systems to prevent their misuse in criminal activities.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co/
Youtube: @thebitcoinlibertarian
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
Get Orange Pill App And Connect With Bitcoiners In Your Area. Stack Friends Who Stack Sats link: https://signup.theorangepillapp.com/opa/croxroad
Buy Bitcoin Books At Konsensus Network Store. 10% Discount With Code “21croxroad” link: https://bitcoinbook.shop?ref=21croxroad
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ fcd81845:5c1832a7
2025-03-07 09:25:39
@ fcd81845:5c1832a7
2025-03-07 09:25:39Price Updates
In order to improve the services we offer, we are increasing the prices effective date March 6th 2025:
Here are the price changes (all prices are per month, rolling contract):
| name | Price | New Price | | ---- | ----- | --------- | | Tiny | 2 EUR | 2.70 EUR | | Small | 4 EUR | 5.10 EUR | | Medium | 8 EUR | 9.90 EUR | | Large | 17 EUR | 21.90 EUR | | X-Large | 30 EUR | 39.90 EUR | | XX-Large | 45 EUR | 55.50 EUR |
These changes coincide with the release of custom pricing!

We have also released a few other features:
- User configurable PTR records
- Separate billing page o VM info view
- VM resource usage graphs
- New VM's are assigned a forward DNS entry on lnvps.cloud (eg. vm-1.lnvps.cloud) existing VM's will have a forward entry added at a later date.
- As well as many other smaller improvements in the handling of resource allocation
-
 @ 95cb4330:96db706c
2025-03-07 07:21:49
@ 95cb4330:96db706c
2025-03-07 07:21:49Embracing Contrarian Thinking, as advocated by Peter Thiel, involves challenging prevailing beliefs to uncover unique opportunities and minimize competition. This mindset encourages asking:
"What important truth do very few people agree with me on?"
By doing so, individuals and organizations can identify untapped markets and innovate beyond conventional boundaries.
Understanding Contrarian Thinking
- Definition:
A mindset that involves questioning widely accepted norms and beliefs to discover unique insights and opportunities.
Examples in Practice
-
Peter Thiel's Investment in Facebook:
Thiel invested in Facebook when social media was largely dismissed as a passing trend, recognizing its potential to revolutionize communication. -
Elon Musk's Development of Tesla:
Musk pursued the development of electric vehicles despite widespread skepticism about their viability, ultimately leading to Tesla's success in the automotive industry. -
Jeff Bezos's Customer-Centric Approach at Amazon:
Bezos prioritized long-term customer satisfaction over immediate profits, a strategy that defied traditional retail models and contributed to Amazon's dominance.
Implementing Contrarian Thinking
-
Challenge Assumptions:
Regularly question the status quo and consider alternative perspectives. -
Embrace Risk:
Be willing to explore unconventional ideas, understanding that innovation often involves venturing into uncharted territory. -
Foster a Diverse Environment:
Encourage diverse viewpoints within your team to stimulate critical thinking and challenge groupthink.
Benefits of Contrarian Thinking
-
Innovation:
By challenging existing paradigms, contrarian thinkers can develop groundbreaking products and services. -
Competitive Advantage:
Identifying opportunities overlooked by others can lead to market leadership. -
Resilience:
A contrarian mindset fosters adaptability, enabling individuals and organizations to navigate changing environments effectively.
Action Step
Identify a commonly held belief in your industry or field. Consider the opposite perspective and explore the potential opportunities that this contrarian viewpoint might reveal.
By adopting contrarian thinking, you position yourself to uncover unique opportunities and drive innovation beyond conventional boundaries.
For further insights into Peter Thiel's approach to contrarian thinking, consider watching this discussion:
Peter Thiel's Contrarian Strategy
- Definition:
-
 @ 3d100e1d:f294e874
2025-03-07 07:00:36
@ 3d100e1d:f294e874
2025-03-07 07:00:36A 68BRL está se destacando no mundo dos jogos digitais, oferecendo uma experiência única e inovadora para seus usuários. Com um design moderno e intuitivo, a plataforma foi desenvolvida para garantir uma navegação simples e uma experiência agradável desde o momento em que o jogador entra no site. Se você está procurando uma plataforma de jogos online confiável e dinâmica, a 68BRL é a escolha ideal.
O foco principal da plataforma é proporcionar uma experiência de entretenimento de qualidade. Com segurança aprimorada e um sistema de transações ágil, os jogadores podem relaxar enquanto se divertem, sabendo que seus dados estão protegidos e suas interações são monitoradas.
Introdução aos Jogos: Qualidade e Diversão ao Seu Alcance
A 68brl oferece uma extensa gama de jogos que atendem a todos os tipos de jogadores. Se você é fã de desafios rápidos e emocionantes ou prefere jogos mais estratégicos e reflexivos, há opções para todos os gostos. Os títulos são desenvolvidos por alguns dos estúdios mais renomados da indústria, garantindo gráficos impressionantes e jogabilidade de alta qualidade.
Entre os jogos mais populares, destacam-se aqueles que exigem raciocínio rápido e habilidades, mas a plataforma também oferece uma variedade de opções mais simples e descontraídas, perfeitas para quem procura algo mais leve.
A cada novo mês, novos títulos são adicionados à plataforma, mantendo a experiência de jogo fresca e empolgante. Torneios e eventos especiais são frequentemente organizados, oferecendo aos jogadores a chance de testar suas habilidades e competir por prêmios incríveis.
Experiência do Jogador: Simples, Divertida e Social
A 68BRL não é apenas uma plataforma para jogar, mas também para interagir. A plataforma valoriza a construção de uma comunidade ativa de jogadores. Você pode se conectar com amigos, formar grupos ou até competir em equipes, proporcionando uma experiência social ainda mais envolvente.
Além disso, a interface é altamente personalizável. Você pode ajustar configurações de jogo, personalizar seu perfil e acessar diferentes títulos com facilidade. A plataforma foi desenhada para garantir que sua experiência de jogo seja fluída, sem dificuldades, e completamente envolvente.
Outro aspecto importante é o suporte ao cliente. A equipe de atendimento da 68BRL está disponível 24/7, pronta para responder a perguntas, resolver problemas técnicos ou ajudar em qualquer outro aspecto relacionado à sua experiência.
Conclusão: Uma Plataforma de Entretenimento Inovadora e Segura
Com sua interface amigável, jogos de alta qualidade e uma experiência social envolvente, a 68BRL se destaca como uma das principais plataformas de entretenimento online. Se você está procurando por diversão, segurança e uma comunidade ativa, esta plataforma tem tudo o que você precisa. Não perca tempo, comece sua jornada na 68BRL e descubra um novo mundo de entretenimento!
-
 @ 3d100e1d:f294e874
2025-03-07 06:59:40
@ 3d100e1d:f294e874
2025-03-07 06:59:40Com o crescimento do entretenimento digital no Brasil, a 188Rio se destaca como uma plataforma confiável e inovadora, oferecendo uma vasta gama de opções para jogadores de todos os estilos. Com um design simples e uma navegação eficiente, a 188Rio permite que qualquer jogador, independentemente de sua experiência, se sinta à vontade desde o momento em que entra na plataforma.
A segurança é um dos principais pilares da 188Rio. Com o uso de tecnologia de ponta, a plataforma protege as informações e transações dos jogadores, garantindo que possam desfrutar da experiência sem preocupações. Além disso, a 188Rio é totalmente otimizada para dispositivos móveis, permitindo que os usuários se divirtam a qualquer hora e em qualquer lugar.
Variedade de Jogos e Entretenimento:
A 188rio oferece uma impressionante variedade de jogos, atendendo aos mais diversos gostos e preferências. Se você é fã de slots emocionantes, de jogos de mesa como blackjack, ou até mesmo de simuladores de esportes, a plataforma tem algo para você.
Os jogos de slots são populares por suas histórias envolventes e gráficos de alta qualidade. Com mecânicas de bônus e multiplicadores, os jogadores têm a oportunidade de ganhar prêmios valiosos enquanto exploram diferentes temas, como mitologia, fantasia e aventuras épicas. A 188Rio se esforça para oferecer títulos novos e emocionantes, garantindo uma experiência sempre fresca.
Para aqueles que preferem os clássicos, a 188Rio possui uma série de jogos de mesa, como blackjack e roleta. Essas opções são ideais para jogadores que desejam testar suas habilidades e estratégias, com regras simples e jogabilidade fluida, que garantem diversão sem complicação.
Os simuladores de esportes são outra grande atração. Com eventos esportivos virtuais que simulam competições reais, como futebol, basquete e corridas, os jogadores podem experimentar a adrenalina de uma partida emocionante enquanto tentam prever os resultados e acumular prêmios.
A Experiência do Jogador na 188Rio:
A experiência de jogo na 188Rio é projetada para ser agradável e livre de estresse. A plataforma oferece uma interface clara e objetiva, tornando fácil para os jogadores encontrar o que procuram. A navegação intuitiva permite que qualquer jogador, seja novato ou experiente, aproveite os jogos sem complicações.
O suporte ao cliente é outro ponto forte da plataforma. Com uma equipe eficiente disponível 24/7, a 188Rio garante que qualquer dúvida ou problema seja rapidamente resolvido, proporcionando uma experiência tranquila para os jogadores.
Além disso, a 188Rio oferece várias promoções e bônus para seus jogadores. Seja para novos usuários ou jogadores frequentes, as ofertas especiais aumentam ainda mais as chances de diversão e de ganho, criando um ambiente ainda mais dinâmico e recompensador.
Conclusão:
A 188Rio é uma plataforma completa e segura para quem busca diversão, entretenimento de qualidade e uma experiência sem preocupações. Com uma variedade de jogos e recursos que atendem a todos os gostos, a plataforma é uma das melhores opções para quem deseja se divertir e testar sua sorte em um ambiente digital confiável.
-
 @ 3d100e1d:f294e874
2025-03-07 06:58:21
@ 3d100e1d:f294e874
2025-03-07 06:58:21A AA999 é uma plataforma inovadora de entretenimento online que oferece uma vasta gama de jogos, desde os mais tradicionais até as opções mais modernas e dinâmicas. Seja você um jogador experiente ou um novato no mundo dos jogos online, a AA999 é a escolha ideal para quem busca diversão, emoção e desafios constantes.
Plataforma de Acesso Simples e Funcional Um dos maiores atrativos da AA999 é sua simplicidade. A plataforma foi desenvolvida para ser acessível a todos os usuários, independentemente de sua experiência prévia. Seu layout intuitivo permite que qualquer jogador navegue facilmente entre os diversos jogos e opções, garantindo uma experiência fluída e agradável.
Além disso, a AA999 conta com um sistema de segurança de ponta, que utiliza criptografia avançada para proteger os dados dos usuários. Isso garante que as informações pessoais e financeiras dos jogadores sejam mantidas em total sigilo, criando um ambiente seguro para que todos se concentrem no que mais importa: a diversão.
Variedade de Jogos para Todos os Gostos AA999 oferece uma impressionante variedade de jogos, adaptados para os mais diversos estilos de jogador. Se você gosta de jogos de estratégia e raciocínio, a plataforma oferece diversas opções de jogos de mesa, como poker, blackjack e roleta. Esses jogos são ideais para quem deseja testar suas habilidades e aperfeiçoar suas táticas.
Para os jogadores que preferem algo mais rápido e empolgante, a AA999 oferece uma ampla seleção de jogos de sorte. Esses jogos permitem que o jogador viva momentos de pura adrenalina, com resultados rápidos e imprevisíveis. A plataforma também é constantemente atualizada, garantindo que novos títulos sejam adicionados regularmente para que os jogadores nunca se sintam entediados.
A Experiência do Jogador na AA999 A experiência de jogo na AA999 é projetada para ser completamente imersiva e divertida. Com gráficos modernos e animações fluidas, os jogos da plataforma proporcionam uma jogabilidade de alta qualidade. Além disso, a plataforma é compatível com diversos dispositivos, permitindo que os jogadores aproveitem suas opções favoritas tanto no desktop quanto no celular.
Outro aspecto que torna a experiência do jogador ainda mais atraente é o sistema de recompensas. A AA999 oferece bônus de boas-vindas, promoções sazonais e até programas de fidelidade, onde os jogadores podem acumular pontos e trocá-los por benefícios exclusivos. Esse sistema de recompensas é uma forma de incentivar os jogadores a explorar novos jogos e continuar jogando.
Suporte de Qualidade ao Jogador A AA999 também se destaca pelo seu atendimento ao cliente. Com uma equipe de suporte eficiente e pronta para ajudar, a plataforma oferece assistência 24 horas por dia, sete dias por semana. Seja para solucionar um problema técnico ou tirar dúvidas sobre os jogos, os jogadores sempre terão ajuda disponível.
Conclusão A AA999 é uma plataforma de entretenimento online que oferece uma experiência completa para todos os jogadores. Com sua interface amigável, segurança robusta, diversidade de jogos e excelente suporte ao cliente, a plataforma é uma das melhores opções no mercado para quem busca diversão e emoção. Experimente a AA999 e descubra um novo mundo de entretenimento online.
-
 @ da0b9bc3:4e30a4a9
2025-03-07 06:27:17
@ da0b9bc3:4e30a4a9
2025-03-07 06:27:17Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/906261
-
 @ d360efec:14907b5f
2025-03-07 05:11:52
@ d360efec:14907b5f
2025-03-07 05:11:52Bitcoin (BTC) เผชิญกับการปรับฐานอย่างรุนแรงในวันที่ 7 มีนาคม 2568 หลังจากที่ราคาพุ่งขึ้นทำจุดสูงสุดใหม่ (All-Time High) อย่างต่อเนื่อง บทวิเคราะห์นี้จะเจาะลึกถึงสถานการณ์ปัจจุบันของ BTC โดยใช้การวิเคราะห์ทางเทคนิคจากหลาย Timeframe (15m, 4H, Day) พร้อมทั้งพิจารณาอินดิเคเตอร์สำคัญต่างๆ เพื่อประเมินแนวโน้มและกลยุทธ์การเทรดที่เหมาะสม
การวิเคราะห์ทางเทคนิค:
-
Timeframe 15 นาที (15m):
- เกิดการร่วงลงของราคาอย่างรุนแรง (Sell-Off) ทะลุแนวรับสำคัญหลายระดับ
- EMA 50 ตัด EMA 200 ลงมา (Death Cross) เป็นสัญญาณ Bearish ที่ชัดเจน
- Money Flow เป็นลบอย่างมาก
- Trend Strength เป็นเมฆสีแดงหนาแน่น (แนวโน้มขาลงแข็งแกร่ง)
- สรุป: แนวโน้มขาลงระยะสั้นชัดเจน
-
Timeframe 4 ชั่วโมง (4H):
- ราคาหลุดกรอบ Consolidation และ EMA 50
- EMA 50 ตัด EMA 200 ลงมา (Death Cross) ยืนยันสัญญาณ Bearish ระยะกลาง
- Money Flow เป็นลบ
- Trend Strength เป็นเมฆสีแดง
- แนวรับสำคัญอยู่ที่ EMA 200 (ประมาณ $60,000) และ $58,000
- สรุป: ยืนยันการปรับฐานระยะกลาง
-
Timeframe Day (Day):
- ราคายังคงอยู่เหนือ EMA 50 และ EMA 200 โครงสร้างขาขึ้นหลักยังไม่เสีย
- Money Flow ยังคงเป็นบวก (แม้จะเริ่มลดลง)
- Trend Strength เมฆสีเขียวยังคงอยู่ (แต่เริ่มบางลง)
- แนวรับสำคัญอยู่ที่ $60,000 (Low ก่อนหน้า) และ $50,000-$52,000 (EMA 200 และ Demand Zone)
- สรุป: แนวโน้มระยะยาวยังเป็นขาขึ้น แต่เริ่มมีสัญญาณอ่อนแรง
Buyside & Sellside Liquidity (สรุปจากทุก TF):
- Buyside Liquidity (แนวต้าน): $68,000-$69,000 (แนวต้านที่แข็งแกร่งในระยะสั้น), $72,000, $75,000 (เป้าหมายระยะยาว หากกลับเป็นขาขึ้น)
- Sellside Liquidity (แนวรับ): $60,000 (แนวรับสำคัญทางจิตวิทยา และ EMA 200 ใน TF 4H, Low ก่อนหน้าใน TF Day), $58,000 (Demand Zone ใน TF 4H), $50,000-$52,000 (EMA 200 และ Demand Zone ใน TF Day)
กลยุทธ์การเทรด:
- Day Trade (15m): ความเสี่ยงสูงมาก ไม่แนะนำให้ Buy เน้น Short Sell เมื่อราคา Rebound ขึ้นไปทดสอบแนวต้าน (EMA หรือบริเวณ $68,000-$69,000) และมีสัญญาณ Bearish แต่ต้องระมัดระวังอย่างยิ่ง เพราะขัดแย้งกับแนวโน้มหลักระยะยาว ตั้ง Stop Loss เหนือ Swing High
- Swing Trade (4H): ไม่แนะนำให้ Buy ตอนนี้ รอสัญญาณกลับตัวที่ชัดเจนกว่านี้ บริเวณแนวรับ EMA 200 ($60,000) หรือ $58,000 หากมีสัญญาณ Bullish ที่แนวรับเหล่านี้ ถึงจะพิจารณาเข้า Buy โดยตั้ง Stop Loss ต่ำกว่าแนวรับ
- Position Trade (Day): รอจังหวะที่แนวรับสำคัญ ($60,000 หรือ $50,000-$52,000) หรือรอสัญญาณกลับตัวที่ชัดเจน
สิ่งที่ต้องระวัง:
- ความผันผวนของราคา BTC ที่สูงมากในช่วงนี้
- ข่าวหรือเหตุการณ์ที่อาจส่งผลกระทบต่อตลาด
- False Breakout และ Dead Cat Bounce (การ Rebound สั้นๆ ก่อนลงต่อ)
- การสวน Trend มีความเสี่ยงสูงมาก
สรุป:
Bitcoin กำลังเผชิญกับการปรับฐานครั้งสำคัญ หลังจากที่ราคาพุ่งขึ้นอย่างต่อเนื่อง แนวโน้มระยะสั้น (15m) เป็นขาลงอย่างชัดเจน, ระยะกลาง (4H) ยืนยันการปรับฐาน, ส่วนระยะยาว (Day) ยังคงเป็นขาขึ้นแต่เริ่มอ่อนแรง นักลงทุนควรใช้ความระมัดระวังอย่างสูงในการเทรด Day Trader อาจพิจารณา Short Sell เมื่อมีสัญญาณ, Swing Trader ควรรอสัญญาณกลับตัวที่แนวรับ, ส่วน Position Trader ควรรอจังหวะที่แนวรับสำคัญ
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
-
 @ d360efec:14907b5f
2025-03-07 05:08:51
@ d360efec:14907b5f
2025-03-07 05:08:51$OKX: $BTC $USDT.P
Introduction:
Bitcoin (BTC) faced a sharp correction on March 7, 2025, after a continuous rally to new all-time highs. This analysis delves into the current situation of BTC using technical analysis from multiple timeframes (15m, 4H, Day), considering various key indicators to assess the trend and appropriate trading strategies.
Technical Analysis:
-
15-Minute Timeframe (15m):
- Experienced a sharp price drop (Sell-Off), breaking through several key support levels.
- EMA 50 crossed below EMA 200 (Death Cross), a clear Bearish signal.
- Money Flow is strongly negative.
- Trend Strength is a thick red cloud (strong downtrend).
- Conclusion: Clear short-term downtrend.
-
4-Hour Timeframe (4H):
- Price broke out of the consolidation range and below EMA 50.
- EMA 50 crossed below EMA 200 (Death Cross), confirming a medium-term Bearish signal.
- Money Flow is negative.
- Trend Strength is a red cloud.
- Key support is at EMA 200 (around $60,000) and $58,000.
- Conclusion: Confirms the medium-term correction.
-
Daily Timeframe (Day):
- The price remains above EMA 50 and EMA 200. The main uptrend structure is still intact.
- Money Flow remains positive (although starting to decrease).
- Trend Strength: The green cloud is still present (but starting to thin).
- Key support is at $60,000 (previous Low) and $50,000-$52,000 (EMA 200 and Demand Zone).
- Conclusion: The long-term trend is still uptrend, but signs of weakness are starting to appear.
Buyside & Sellside Liquidity (Summary from all TFs):
- Buyside Liquidity (Resistance): $68,000-$69,000 (strong resistance in the short term), $72,000, $75,000 (long-term targets if it turns bullish again).
- Sellside Liquidity (Support): $60,000 (key psychological support and EMA 200 on 4H TF, previous Low on Day TF), $58,000 (Demand Zone on 4H TF), $50,000-$52,000 (EMA 200 and Demand Zone on Day TF).
Trading Strategies:
- Day Trade (15m): Very high risk. Do not recommend Buy. Focus on Short Selling when the price rebounds to test resistance (EMA or the $68,000-$69,000 area) and there are Bearish signals. But be extremely careful as it contradicts the main long-term trend. Set a Stop Loss above the Swing High.
- Swing Trade (4H): Do not Buy now. Wait for clearer reversal signals around the EMA 200 support ($60,000) or $58,000. If there are Bullish signals at these supports, then consider entering a Buy with a Stop Loss below the support.
- Position Trade (Day): Wait for opportunities at key support levels ($60,000 or $50,000-$52,000) or wait for clear reversal signals.
Things to Watch Out For:
- Very high volatility of BTC price during this period.
- News or events that may affect the market.
- False Breakouts and Dead Cat Bounces (short rebounds before continuing to fall).
- Going against the trend is very high risk.
Summary:
Bitcoin is facing a significant correction after a continuous rally. The short-term trend (15m) is clearly bearish, the medium-term (4H) confirms the correction, while the long-term (Day) is still bullish but starting to weaken. Investors should be extremely cautious in trading. Day traders may consider Short Selling on signal, Swing traders should wait for reversal signals at support, and Position traders should wait for opportunities at key support levels.
Disclaimer: This analysis is a personal opinion and not investment advice. Investors should do their own research and make decisions carefully.
-
-
 @ 527b02f7:b0ed5fd2
2025-03-07 21:40:48
@ 527b02f7:b0ed5fd2
2025-03-07 21:40:48202502181044 Este HUD para PLO debería de estar prohibido☠⛔
Creado: 2025-02-18 10:46
La estructura del HUD: La esencia de la información para explotar a tus rivales 📊
Un HUD para PLO debe reunir estadísticas específicas y bien calibradas, pensadas para identificar patrones de juego y explotar las debilidades de cada rival. Este en particular incluye todas las métricas que considero esenciales.
Dependiendo de tu nivel tienes disponibles dos versiones del HUD:
- Una para PLO BASIC, más sencilla con los valores esenciales generales y los valores más básicos post-flop
![[Pasted image 20250218105241.png]]
- Otra para PLO PRO, la versión más completa con toda la información necesaria que necesitas para conocer cada detalle del juego de tus rivales.
![[Hand2Note_Zr1rE8CUv7.png]]
Todo HUD comienza con las tres estadísticas generales más importantes para identificar a qué tipo de jugador te enfrentas:
- VPIP (Voluntarily Put Money In Pot): Esta estadística muestra la frecuencia con la que un jugador pone dinero en el bote de forma voluntaria.
- PFR (Preflop Raise): Un indicador de la agresividad preflop. El PFR nos permite entender qué tan seguido un jugador toma la iniciativa antes del flop, lo que es esencial para decidir cuándo hacer call o re-raise.
- 3-Bet Preflop: la frecuencia de 3-bet preflop nos indica el % de manos que está resubiendo el jugador pre-flop. Esto nos indica su grado de agresividad general antes del flop.
Esto como puedes imaginarte es tan solo un aperitivo de todo lo que podemos deducir de las estadísticas que nos da el HUD.
Instalación y configuración del HUD en cada software 🔧
Configurar el HUD en Hand2Note, PT4 o HM3 es bastante sencillo, y en Mentopoker puedes acceder a tutoriales específicos. Estos tutoriales te guiarán paso a paso para que puedas instalarlo correctamente y personalizar algunos ajustes según tu estilo de juego.
Puedes descargar el HUD en sus dos versiones dependiendo de tu nivel en la escuela directamente desde la página de descargas de Mentopoker.
Además si quieres aprender a leer, interpretar y sacar el máximo provecho al HUD, tienes clases específicas en la escuela donde te lo explico con lujo de detalles.
Estás dejando dinero en la mesa 💸
Si estás buscando una herramienta que te dé una ventaja real en las mesas de PLO, este HUD es sin duda una de las mejores opciones. La suscripción a Mentopoker no solo te permitirá acceder a este HUD, sino que también podrás mejorar cada aspecto de tu juego con el soporte y las clases exclusivas que hemos creado.
Si quieres jugar como un profesional y ganar como un profesional, has de usar las herramientas que usan los profesionales. Un HUD mediocre te brindará información poco precisa y dejará muchos huecos de información sobre información relevante. Por el contrario un HUD hecho por jugadores profesionales, te dará información crucial que marcará la diferencia en decisiones clave, que te harán incrementar sin lugar a dudas tu winrate.
En la escuela siempre compartimos los métodos y herramientas que usamos nosotros en las mesas día a día, para que así siempre tengas los mejores recursos a tu disposición.
En futuros artículos compartiré otra información relevante al respecto, como la fiabilidad de los datos y el grado de certeza de las muestras.
¡Nos vemos en las mesas!
Suscríbete al blog.
Te informaré cada vez que publique una nueva entrada y así estarás al día de las últimas novedades.
El email que proporciones no se utilizará para mandar publicidad, ni se compartirá con terceros. Solo se te enviarán todas las novedades de esta web.
-
 @ c48e29f0:26e14c11
2025-03-07 04:51:09
@ c48e29f0:26e14c11
2025-03-07 04:51:09ESTABLISHMENT OF THE STRATEGIC BITCOIN RESERVE AND UNITED STATES DIGITAL ASSET STOCKPILE EXECUTIVE ORDER March 6, 2025
By the authority vested in me as President by the Constitution and the laws of the United States of America, it is hereby ordered:
Section 1. Background.
Bitcoin is the original cryptocurrency. The Bitcoin protocol permanently caps the total supply of bitcoin (BTC) at 21 million coins, and has never been hacked. As a result of its scarcity and security, Bitcoin is often referred to as “digital gold”. Because there is a fixed supply of BTC, there is a strategic advantage to being among the first nations to create a strategic bitcoin reserve. The United States Government currently holds a significant amount of BTC, but has not implemented a policy to maximize BTC’s strategic position as a unique store of value in the global financial system. Just as it is in our country’s interest to thoughtfully manage national ownership and control of any other resource, our Nation must harness, not limit, the power of digital assets for our prosperity.
Sec. 2. Policy.
It is the policy of the United States to establish a Strategic Bitcoin Reserve. It is further the policy of the United States to establish a United States Digital Asset Stockpile that can serve as a secure account for orderly and strategic management of the United States’ other digital asset holdings.
Sec. 3. Creation and Administration of the Strategic Bitcoin Reserve and United States Digital Asset Stockpile.
(a) The Secretary of the Treasury shall establish an office to administer and maintain control of custodial accounts collectively known as the “Strategic Bitcoin Reserve,” capitalized with all BTC held by the Department of the Treasury that was finally forfeited as part of criminal or civil asset forfeiture proceedings or in satisfaction of any civil money penalty imposed by any executive department or agency (agency) and that is not needed to satisfy requirements under 31 U.S.C. 9705 or released pursuant to subsection (d) of this section (Government BTC). Within 30 days of the date of this order, each agency shall review its authorities to transfer any Government BTC held by it to the Strategic Bitcoin Reserve and shall submit a report reflecting the result of that review to the Secretary of the Treasury. Government BTC deposited into the Strategic Bitcoin Reserve shall not be sold and shall be maintained as reserve assets of the United States utilized to meet governmental objectives in accordance with applicable law.
(b) The Secretary of the Treasury shall establish an office to administer and maintain control of custodial accounts collectively known as the “United States Digital Asset Stockpile,” capitalized with all digital assets owned by the Department of the Treasury, other than BTC, that were finally forfeited as part of criminal or civil asset forfeiture proceedings and that are not needed to satisfy requirements under 31 U.S.C. 9705 or released pursuant to subsection (d) of this section (Stockpile Assets). Within 30 days of the date of this order, each agency shall review its authorities to transfer any Stockpile Assets held by it to the United States Digital Asset Stockpile and shall submit a report reflecting the result of that review to the Secretary of the Treasury. The Secretary of the Treasury shall determine strategies for responsible stewardship of the United States Digital Asset Stockpile in accordance with applicable law.
(c) The Secretary of the Treasury and the Secretary of Commerce shall develop strategies for acquiring additional Government BTC provided that such strategies are budget neutral and do not impose incremental costs on United States taxpayers. However, the United States Government shall not acquire additional Stockpile Assets other than in connection with criminal or civil asset forfeiture proceedings or in satisfaction of any civil money penalty imposed by any agency without further executive or legislative action.
(d) “Government Digital Assets” means all Government BTC and all Stockpile Assets. The head of each agency shall not sell or otherwise dispose of any Government Digital Assets, except in connection with the Secretary of the Treasury’s exercise of his lawful authority and responsible stewardship of the United States Digital Asset Stockpile pursuant to subsection (b) of this section, or pursuant to an order from a court of competent jurisdiction, as required by law, or in cases where the Attorney General or other relevant agency head determines that the Government Digital Assets (or the proceeds from the sale or disposition thereof) can and should: (i) be returned to identifiable and verifiable victims of crime; (ii) be used for law enforcement operations;
(iii) be equitably shared with State and local law enforcement partners; or (iv) be released to satisfy requirements under 31 U.S.C. 9705, 28 U.S.C. 524(c), 18 U.S.C. 981, or 21 U.S.C. 881.(e) Within 60 days of the date of this order, the Secretary of the Treasury shall deliver an evaluation of the legal and investment considerations for establishing and managing the Strategic Bitcoin Reserve and United States Digital Asset Stockpile going forward, including the accounts in which the Strategic Bitcoin Reserve and United States Digital Asset Stockpile should be located and the need for any legislation to operationalize any aspect of this order or the proper management and administration of such accounts.
Sec. 4. Accounting.
Within 30 days of the date of this order, the head of each agency shall provide the Secretary of the Treasury and the President’s Working Group on Digital Asset Markets with a full accounting of all Government Digital Assets in such agency’s possession, including any information regarding the custodial accounts in which such Government Digital Assets are currently held that would be necessary to facilitate a transfer of the Government Digital Assets to the Strategic Bitcoin Reserve or the United States Digital Asset Stockpile. If such agency holds no Government Digital Assets, such agency shall confirm such fact to the Secretary of the Treasury and the President’s Working Group on Digital Asset Markets within 30 days of the date of this order.
Sec. 5. General Provisions.
(a) Nothing in this order shall be construed to impair or otherwise affect: (i) the authority granted by law to an executive department or agency, or the head thereof; or (ii) the functions of the Director of the Office of Management and Budget relating to budgetary, administrative, or legislative proposals.
(b) This order shall be implemented consistent with applicable law and subject to the availability of appropriations.
(c) This order is not intended to, and does not, create any right or benefit, substantive or procedural, enforceable at law or in equity by any party against the United States, its departments, agencies, or entities, its officers, employees, or agents, or any other person.
THE WHITE HOUSE, March 6, 2025
-
 @ 49814c0f:72d54ea1
2025-03-07 03:07:46
@ 49814c0f:72d54ea1
2025-03-07 03:07:46Fiber is a Lightning-compatible peer-to-peer payment and swap network built on CKB, the base layer of Nervos Network. Fiber is designed to enable fast, secure, and efficient off-chain payment solutions, particularly for micropayments and high-frequency transactions.
Inspired by Bitcoin’s Lightning Network, Fiber leverages CKB’s unique architecture and offers the following key features:
- Multi-Asset Support: Fiber is not limited to a single currency; it supports transactions involving multiple assets, paving the way for complex cross-chain financial applications.
- Cross-Chain Interoperability: Fiber is natively designed to interact with Lightning Networks on other UTXO-based blockchains (such as Bitcoin), improving cross-chain asset liquidity and network compatibility.
- Flexible State Management: Thanks to CKB’s Cell model, Fiber efficiently manages channel states, reducing the complexity of off-chain interactions.
- Programmability: Built on CKB’s Turing-complete smart contracts architecture, Fiber enables more complex conditional execution and transaction rules, extending the use cases of payment channels.
This article presents a source code-level exploration of Fiber's architecture, key modules, as well as an overview of its future development plans.
Prerequisites
- Rust and Actor Framework: Fiber is entirely implemented in Rust and follows the Actor Model programming paradigm. It relies on the community-maintained slawlor/ractor framework.
- Lightning Network: Fiber follows the core principles of Lightning Network. Resources such as Mastering the Lightning Network and BOLTs are highly recommended for understanding the concepts.
- CKB Transactions and Contracts: Fiber interacts with CKB nodes via RPC, making a solid understanding of CKB contract development essential.
Key Modules
At a high level, a Fiber node consists of several key modules:

Overview
- Network Actor: Facilitates communication between nodes and channels, managing both internal and external messages along with related management operations.
- Network Graph: Maintains a node’s view of the entire network, storing data on all nodes and channels while dynamically updating through gossip messages. When receiving a payment request, a node uses the network graph to find a route to the recipient.
- PaymentSession: Manages the lifecycle of a payment.
- fiber-sphinx : A Rust library for Onion packet encryption and decryption. In Fiber, this ensures sensitive payment details are hidden from intermediate nodes, enhancing security and anonymity.
- Gossip: A protocol for sharing channel/node information, facilitating payment path discovery and updates.
- Watchtower: Monitors channels for fraudulent transactions. If a peer submits an outdated commitment transaction, the watchtower issues a revocation transaction as a penalty.
- Cross Hub: Enables cross-chain interoperability. For example, a payer can send Bitcoin through the Lightning Network, while the recipient receives CKB. The cross hub handles the conversion, mapping Bitcoin payments and invoices to Fiber’s system.
- Fiber-Scripts: A separate repository containing two main contracts:
- Funding Lock: A contract for locking funds, utilizing the
ckb-authlibrary to implement a 2-of-2 multi-signature scheme for channel funding. - Commitment Lock: Implements the Daric protocol as Fiber’s penalty mechanism to achieve optimal storage and bounded closure.
- Funding Lock: A contract for locking funds, utilizing the
Efficient Channel Management with the Actor Model
The Lightning Network is essentially a peer-to-peer (P2P) system, where nodes communicate via network messages, updating internal states accordingly. The Actor Model aligns well with this setup:

One potential concern with the Actor Model is its memory footprint and runtime efficiency. We conducted a performance test, showing that 0.9 GB of memory can support 100,000 actors (each with a 1 KB state), processing 100 messages per actor within 10 seconds—demonstrating acceptable performance.
Unlike
rust-lightning, which relies on complex locking mechanisms to maintain data consistency, Fiber’s Actor Model simplifies implementation by eliminating the need for locks to protect data updates. Messages are processed sequentially in an actor’s message queue. When a message handler completes its tasks, the updated channel state is written to the database, streamlining the persistence process.Almost all modules in Fiber use the Actor Model. The Network Actor handles communication both within and across nodes. For example, if Node A wants to send an "Open Channel" message to Node B, the process follows these steps:
- The
Channel Actorin Node A (Actor 0in this case) sends the message to theNetwork Actorin Node B. - The
Network Actortransmits the message using Tentacle, a lower-level networking layer. - The
Network Actorin Node B receives the message and forwards it to the correspondingChannel Actor(Actor 0/1/…/n).

For each new channel, Fiber creates a corresponding ChannelActor, where the
ChannelActorStatemaintains all the necessary data for the channel.Another major advantage of the Actor Model is its ability to map HTLC (Hash Time-Locked Contracts)-related operations directly to specific functions. For example, in the process of forwarding an HTLC across multiple nodes:
- Node A’s
Actor 0handles theAddTlcoperation via handle_add_tlc_command. - Node B’s
Actor 1handles the corresponding peer message via handle_add_tlc_peer_message.

The HTLC management within channels is one of the most complex aspects of the Lightning Network, primarily due to the dependency of channel state changes on peer interactions. Both sides of a channel can have simultaneous HTLC operations.
Fiber adopts
rust-lightning’s approach of using a state machine to track HTLC states, where state transitions occur based oncommitment_signandrevoke_and_ackmessages. TheAddTlcoperation and state transitions for both peers are as follows:
Optimized Payment Processing and Multi-Hop Routing
Each Fiber node maintains a representation of the network through a Network Grap, essentially a bidirectional directed graph, where:
- Each Fiber node represents a vertex.
- Each channel represents an edge.
For privacy reasons, the actual balance partition of a channel is not broadcasted across the network. Instead, the edge weight represents the channel capacity.
Before initiating a payment, the sender performs pathfinding to discover a route to the recipient. If multiple paths available, the sender must determine the optimal one by considering various factors. Finding the best path in a graph with incomplete information is a complex engineering challenge. A detailed discussion of this issue can be found in Mastering Lightning Network.

In Fiber, users initiate payments via RPC requests. When a node receives a payment request, it creates a corresponding PaymentSession to track the payment lifecycle.
The quality of pathfinding directly impacts network efficiency and payment success rates. Currently, Fiber uses a variant of Dijkstra’s algorithm. The implementation can be found here.
However, unlike the standard Dijkstra algorithm, Fiber’s routing expands backward from the target toward the source. During the search, the algorithm considers multiple factors:
- Payment success probability
- Transaction fee
- HTLC lock time
Routes are ranked by computing a distance metric. Probability estimation is derived from past payment results and analysis, implemented in the eval_probability module.
Once the path is determined, the next step is to construct an Onion Packet. Then the source node sends an AddTlcCommand to start the payment. The payment status will be updated asynchronously. Whether the HTLC succeeds or fails, the network actor processes the result via event notifications.
Reliable Payment Retries and Failure Handling
Payments in Fiber may require multiple retries due to various factors, with a common failure scenario being:
- The channel capacity used in the Network Graph is an upper bound.
- The actual available liquidity might be insufficient to complete the payment.
When a payment fails due to liquidity constraints:
- The system returns an error and updates the Network Graph.
- The node automatically initiates a new pathfinding attempt.
This dynamic retry mechanism ensures that payments have a higher chance of success despite fluctuating network conditions.
Peer Broadcasting with Gossip Protocol
Fiber nodes exchange information about new nodes and channels by broadcasting messages. The Gossip module implements the routing gossip protocol defined in BOLTs 7. The key technical decisions were documented in the PR: Refactor gossip protocol.
When a node starts for the first time, it connects to its initial peers using addresses specified in the configuration file under
bootnode_addrs.Fiber supports three types of broadcast messages:
NodeAnnouncementChannelAnnouncementChannelUpdate
The raw broadcast data received is stored in the storage module, allowing messages to be efficiently indexed using a combination of
timestamp + message_id. This enables quicker responses to query requests from peer nodes.When a node starts, the Graph module loads all stored messages using load_from_store to rebuild its network graph.
Fiber propagates gossip messages using a subscription-based model.
- A node actively sends a broadcast message filter (
BroadcastMessagesFilter) to a peer. - When the peer receives this filter, it creates a corresponding PeerFilterActor, which subscribes to gossip messages.
This subscription model allows nodes to efficiently receive newly stored gossip messages after a specific cursor, enabling them to dynamically update their network graph, because the network graph also subscribes to gossip messages. The logic for retrieving these messages is implemented in this section.
Enhancing Privacy with Onion Encryption & Decryption
For privacy and security consideration, payments’ TLC is propagated across multiple nodes using Onion encryption. Each node only accesses the minimal necessary details, such as:
- The amount of the received TLC
- The expiry of the TLC
- The next node in the payment route
This approach ensures that a node cannot access other sensitive details, including the total length of the payment route. The payment sender encrypts the payment details using onion encryption, and each hop must obfuscate the information before forwarding the TLC to the next node.
In case of an error occurs at any hop during payment forwarding, the affected node sends back an error message along the reverse route to the sender. This error message is also onion-encrypted, ensuring that intermediate nodes cannot decipher its content—only the sender can decrypt it.
We examined the onion packet implementation in rust-lightning and found it to be tightly coupled with rust-lightning’s internal data structures, limiting its generalization. Therefore, we built fiber-sphinx from scratch. For more details, refer to the project spec and the developer’s presentation slides.
The key Onion Encryption & Decryption steps in Fiber include:
-
Creating the Onion Packet for Sending Payments
Before sending a payment, the sender creates an onion packet, included in the
AddTlcCommandsent to the first node in the payment route. -
Onion Decryption at Each Hop
- When a node in the payment route receives a TLC, it decrypts one layer of the onion packet, similar to peeling an onion.
- If the node is the final recipient, it processes the payment settlement logic.
- If the node is not the recipient, it continues processing the TLC and then forwards the remaining onion packet to the next hop.
-
Generating an Onion Packet for Error Messages
If an error occurs during TLC forwarding, the node creates a new onion packet containing the error message and sends it back to the previous node.
-
Decrypting Error Messages at the Payment Sender
When the sender receives a TLC fail event, it decrypts the onion packet containing the error. Based on the error details, the sender can decide whether to resend and update the network graph accordingly.

Preventing Channels from Fraud via Watchtower
Watchtower is an important security mechanism in the Lightning Network, primarily used to protect offline users from potential fund theft. It maintains fairness and security by real-time monitoring on-chain transactions and executing penalty transactions when violations are detected.
Fiber's watchtower implementation is in the WatchtowerActor. This actor listens for key events in the Fiber node. For example:
- When a new channel is created, it receives a
RemoteTxCompleteevent, while the watchtower inserts a corresponding record into the database to start monitoring this channel. - When the channel is closed through upon mutual agreement, it receives a
ChannelClosedevent, while the watchtower removes the corresponding record from the database.
During TLC interactions in the channel, the watchtower receives
RemoteCommitmentSignedandRevokeAndAckReceivedevents, updating therevocation_dataandsettlement_datastored in the database respectively. These fields will be used later to create revocation and settlement transactions.Watchtower's penalty mechanism ensures that old commitment transactions are not used in a on-chain transaction by comparing the
commitment_number. If a violation is detected, the watchtower constructs a revocation transaction and submits it on-chain to penalize the offender. Otherwise, it constructs and sends a settlement transaction.Other Technical Decisions
- Storage: We use RocksDB as the storage layer, leveraging its scheme-less storage design to simplify encoding and decoding structs with
serde. Data migration remains a challenge, which we address by this standalone program. - Serialization: Messages between nodes are serialized and deserialized using Molecule, bringing efficiency, compatibility, and security advantages. It ensures determinism, meaning the same message serializes identically on all nodes, which is crucial for signature generation and verification.
Future Prospects
Fiber is still in the early stages of active development. Looking ahead, we plan to make further improvements in the following areas:
- Fix unhandled corner cases to enhance overall robustness;
- Improve the cross-chain hub (currently in the prototype verification stage) by introducing payment session functionality to make cross-chain transactions more user-friendly;
- Refine the payment routing algorithm, potentially introducing multi-path feature and other path-finding strategies to accommodate diverse user preferences and needs;
- Expand contract functionality, including version-based revocation mechanisms and more secure Point Time-Locked Contracts.
-
 @ 3eba5ef4:751f23ae
2025-03-07 02:06:08
@ 3eba5ef4:751f23ae
2025-03-07 02:06:08Crypto Insights
New Direction in Bitcoin’s Post-Quantum Security: Favoring a More Conservative Solution
Bitcoin developer Hunter Beast introduced P2QRH (Pay to Quantum Resistant Hash), an output type, in the earlier proposal BIP 360. However, in a recent post, he indicated that BIP 360 is shifting to supporting algorithms like FALCON, which better facilitate signature aggregation, addressing challenges such as DDoS impact and multisig wallet management. He also emphasized the importance of NIST-certified algorithms for FIPS compliance. He proposed an interim solution called P2TRH (Pay to Taproot Hash), which enables Taproot key-path payments to mitigate quantum security risks.
Notably, this new approach is not a fully quantum-safe solution using post-quantum cryptography. Instead, it is a conservative interim measure: delaying key disclosure until the time of spending, potentially reducing the attack surface from indefinitely exposing elliptic curve public keys on-chain.
BIP 3: New Guidelines for Preparing and Submitting BIPs
BIP 3 Updated BIP Process introduces new guidelines for preparing and submitting BIPs, including updated workflows, BIP formatting, and preamble rules. This update has been merged and replaces the previous BIP 2.
Erlay Implementation in Bitcoin Core: Development Update
Erlay is an alternative transaction relay method between nodes in Bitcoin’s P2P network, designed to reduce bandwidth usage when propagating transaction data.
Bitcoin developer sr-gi summarized the progress of Erlay’s implementation in Bitcoin Core in this article, covering Erlay’s overview, the current implementation approach, thought process, and some open questions.
Dynamic Block Size, Hard Forks, and Sustainability: A Treatise on Bitcoin Block Space Economics
Jameson Lopp examines Bitcoin’s block size debate in this article, arguing that while the controversy has subsided over the past seven years, the discussion remains relevant. Key takeaways include:
-
Simply asserting that the block size should never increase is "intellectually lazy".
-
The core in the block size debate is whether Bitcoin should optimize for low cost of full system validation or low cost of transacting. Bitcoin has chosen the former, so future discussions should focus on maximizing Bitcoin’s user base without disrupting system balance and game theory.
-
A dynamic block size adjustment algorithm could be explored, similar to the difficulty adjustment mechanism, where block size adapts over time based on block space usage and the fee market.
-
Any block size adjustment proposal should include a long-term activation plan—hard fork activation should be gradual to allow most node operators sufficient time to upgrade, reducing the risk of contentious forks.
-
To ensure a sustainable block space market, strategies such as increasing minimum transaction fees or adjusting block space allocation may be necessary—but without inflating the monetary supply.
nAuth: A Decentralized Two Party Authentication and Secure Transmittal Protocol
nAut (or nauth) is a decentralized authentication and document-sharing protocol. By leveraging Nostr’s unique properties, it enables two parties to securely verify identities and exchange documents without relying on a third party—trusted or not.
The motivation behind nAuth is the increasing distrust in intermediaries, which often intercept or reuse user data without consent, sometimes to train AI models or sell to advertisers.
nAuth allows either party to initiate authentication, which is especially useful when one party is device-constrained (e.g., lacks a camera) and unable to scan a QR code or receive an SMS-based authentication.
All Projects Created at Bitcoin++ Hackathon Floripa 2025
The developer-focused conference series Bitcoin++, recently held a hackathon in Florianópolis, Brazil. You can view the 26 projects developed during the event in the project gallery.
Bitkey Introduces Inheritance Feature: Designating Bitcoin Beneficiaries Without Sharing PINs or Seed Phrases
Bitkey has launched an inheritance feature that allows users to designate Bitcoin beneficiaries without risking exposure of PINs or seed phrases during their lifetime or relying on third-party intermediaries.
The feature includes a six-month security period, during which either the user or the designated beneficiary can cancel the inheritance process. After six months, Bitkey will forward the encrypted wrapping key and mobile key to the beneficiary. The beneficiary’s Bitkey app then decrypts the wrapping key using their private key, and subsequently the mobile key. This allows them to co-sign transactions using Bitkey’s servers and transfer the funds to their own Bitkey wallet.
Metamask to Support Solana and Bitcoin
In its announcement titled Reimagining Self-Custody, Metamask revealed plans to support Bitcoin in Q3 of this year, with native Solana support arriving in May.
Key Factors Driving Bitcoin Adoption in 2025
Bitcoin investment platform River has released a report analyzing the key drivers of Bitcoin adoption, Bitcoin protocol evolution, custodial trends, and shifting government policies. Key insights include:
-
Network Health: The Bitcoin network has approximately 21,700 reachable nodes, with hash rate growing 55% in 2024 to 800 EH/s.
-
A Unique Bull Market: Unlike previous cycles, the current market surge is not fueled by global money supply growth (yet) or individuals, but by ETFs and corporate buyers.
-
Ownership Distribution (as of late 2024):
-
Individuals: 69.4%
-
Corporations: 4.4%
-
Funds & ETFs: 6.1%
-
Governments: 1.4%

-
-
Lightning Network Growth: Transaction volume on Lightning increased by 266% in 2024, with fewer transactions overall but significantly higher value per transaction.
-
Shifting Government Policies: More nations are recognizing Bitcoin’s role, with some considering it as a strategic reserve asset. Further pro-Bitcoin policies are expected.
The report concludes that Bitcoin adoption is currently at only 3% of its total potential, with institutional and national adoption expected to accelerate in the coming years.
Top Reads Beyond Blockchain
Beyond 51% Attacks: Precisely Characterizing Blockchain Achievable Resilience
For consensus protocols, what exactly constitutes the "attackers with majority network control"? Is it 51%, 33%, or the 99% claimed by the Dolev–Strong protocol? Decades-old research suggests that the exact threshold depends on the reliability of the communication network connecting validators. If the network reliably transmits messages among honest validators within a short timeframe (call this "synchronous"), it can achieve greater resilience than in cases where the network is vulnerable to partitioning or delays ("partially synchronous").
However, this paper argues that this explanation is incomplete—the final outcome also depends on client modeling details. The study first defines who exactly "clients" are—not just validators participating directly in consensus, but also other roles such as wallet operators or chain monitors. Moreover, their behavior significantly impacts consensus results: Are they "always on" or "sleepy", "silent" or "communicating"?
The research systematizes the models for consensus across four dimensions:
-
Sleepy vs. always-on clients
-
Silent vs. communicating clients
-
Sleepy vs. always-on validators
-
Synchrony vs. partial-synchrony
Based on this classification, the paper systematically describes the achievable safety and liveness resilience with matching possibilities and impossibilities for each of the sixteen models, leading to new protocol designs and impossibility theorems.
Full paper: Consensus Under Adversary Majority Done Right

The Risks of Expressive Smart Contracts: Lessons from the Latest Ethereum Hack
The Blockstream team highlights in this report that the new Bybit exploit in Ethereum smart contracts has reignited long-standing debates about the security trade-offs built into the Ethereum protocol. This incident has drawn attention to the limitations of the EVM—especially its reliance on complex, stateful smart contracts for securing multisig wallets.
The report examines:
-
Systemic challenges in Ethereum’s design: Lack of native multisig, Highly expressive scripting environment, Global key-value store
-
Critical weaknesses of Ethereum’s multisig model
-
A Cautionary Note for expressive smart contracts
The key takeaway is that the more complex a scripting environment, the easier it is to introduce hidden security vulnerabilities. In contrast, Bitcoin's multisig solution is natively built into the protocol, significantly reducing the risk of severe failures due to coding errors. The report argues that as blockchain technology matures, security must be a design priority, not an afterthought.
GitHub Scam Investigation: Thousands of Mods and Cracks Stealing User Data
Despite GitHub’s anti-malware mechanisms, a significant number of malicious repositories persist. This article investigates the widespread distribution of malware on GitHub, disguised as game mods and cracked software, to steal user data. The stolen data—such as crypto wallet keys, bank account, and social media credentials—is then collected and processed on a Discord server, where hundreds of individuals sift through it for valuable information.
Key findings from the investigation include:
-
Distribution method
The author discovered a detailed tutorial explaining how to create and distribute hundreds of malicious GitHub repositories. These repositories masquerade as popular game mods or cracked versions of software like Adobe Photoshop (see image below). The malware aims to collect user logs, including cookies, passwords, IP addresses, and sensitive files.
-
How it works
A piece of malware called "Redox" runs unnoticed in the background, harvesting sensitive data and sending it to a Discord server. It also terminates certain applications (such as Telegram) to avoid detection and uploads files to anonymous file-sharing services like Anonfiles.
By writing a script, the author identified 1,115 repositories generated using the tutorial and compiled the data into this spreadsheet. Surprisingly, fewer than 10% of these repositories had open user complaints, with the rest appearing normal at first glance.
-
-
 @ d34e832d:383f78d0
2025-03-07 01:47:15
@ d34e832d:383f78d0
2025-03-07 01:47:15
A comprehensive system for archiving and managing large datasets efficiently on Linux.
1. Planning Your Data Archiving Strategy
Before starting, define the structure of your archive:
✅ What are you storing? Books, PDFs, videos, software, research papers, backups, etc.
✅ How often will you access the data? Frequently accessed data should be on SSDs, while deep archives can remain on HDDs.
✅ What organization method will you use? Folder hierarchy and indexing are critical for retrieval.
2. Choosing the Right Storage Setup
Since you plan to use 2TB HDDs and store them away, here are Linux-friendly storage solutions:
📀 Offline Storage: Hard Drives & Optical Media
✔ External HDDs (2TB each) – Use
ext4orXFSfor best performance.
✔ M-DISC Blu-rays (100GB per disc) – Excellent for long-term storage.
✔ SSD (for fast access archives) – More durable than HDDs but pricier.🛠 Best Practices for Hard Drive Storage on Linux
🔹 Use
smartctlto monitor drive health
bash sudo apt install smartmontools sudo smartctl -a /dev/sdX🔹 Store drives vertically in anti-static bags.
🔹 Rotate drives periodically to prevent degradation.
🔹 Keep in a cool, dry, dark place.☁ Cloud Backup (Optional)
✔ Arweave – Decentralized storage for public data.
✔ rclone + Backblaze B2/Wasabi – Cheap, encrypted backups.
✔ Self-hosted options – Nextcloud, Syncthing, IPFS.
3. Organizing and Indexing Your Data
📂 Folder Structure (Linux-Friendly)
Use a clear hierarchy:
plaintext 📁 /mnt/archive/ 📁 Books/ 📁 Fiction/ 📁 Non-Fiction/ 📁 Software/ 📁 Research_Papers/ 📁 Backups/💡 Use YYYY-MM-DD format for filenames
✅2025-01-01_Backup_ProjectX.tar.gz
✅2024_Complete_Library_Fiction.epub📑 Indexing Your Archives
Use Linux tools to catalog your archive:
✔ Generate a file index of a drive:
bash find /mnt/DriveX > ~/Indexes/DriveX_index.txt✔ Use
locatefor fast searches:
bash sudo updatedb # Update database locate filename✔ Use
Recollfor full-text search:
bash sudo apt install recoll recoll🚀 Store index files on a "Master Archive Index" USB drive.
4. Compressing & Deduplicating Data
To save space and remove duplicates, use:
✔ Compression Tools:
-tar -cvf archive.tar folder/ && zstd archive.tar(fast, modern compression)
-7z a archive.7z folder/(best for text-heavy files)✔ Deduplication Tools:
-fdupes -r /mnt/archive/(finds duplicate files)
-rdfind -deleteduplicates true /mnt/archive/(removes duplicates automatically)💡 Use
par2to create parity files for recovery:
bash par2 create -r10 file.par2 file.extThis helps reconstruct corrupted archives.
5. Ensuring Long-Term Data Integrity
Data can degrade over time. Use checksums to verify files.
✔ Generate Checksums:
bash sha256sum filename.ext > filename.sha256✔ Verify Data Integrity Periodically:
bash sha256sum -c filename.sha256🔹 Use
SnapRAIDfor multi-disk redundancy:
bash sudo apt install snapraid snapraid sync snapraid scrub🔹 Consider ZFS or Btrfs for automatic error correction:
bash sudo apt install zfsutils-linux zpool create archivepool /dev/sdX
6. Accessing Your Data Efficiently
Even when archived, you may need to access files quickly.
✔ Use Symbolic Links to "fake" files still being on your system:
bash ln -s /mnt/driveX/mybook.pdf ~/Documents/✔ Use a Local Search Engine (Recoll):
bash recoll✔ Search within text files usinggrep:
bash grep -rnw '/mnt/archive/' -e 'Bitcoin'
7. Scaling Up & Expanding Your Archive
Since you're storing 2TB drives and setting them aside, keep them numbered and logged.
📦 Physical Storage & Labeling
✔ Store each drive in fireproof safe or waterproof cases.
✔ Label drives (Drive_001,Drive_002, etc.).
✔ Maintain a printed master list of drive contents.📶 Network Storage for Easy Access
If your archive grows too large, consider:
- NAS (TrueNAS, OpenMediaVault) – Linux-based network storage.
- JBOD (Just a Bunch of Disks) – Cheap and easy expansion.
- Deduplicated Storage –ZFS/Btrfswith auto-checksumming.
8. Automating Your Archival Process
If you frequently update your archive, automation is essential.
✔ Backup Scripts (Linux)
Use
rsyncfor incremental backups:bash rsync -av --progress /source/ /mnt/archive/Automate Backup with Cron Jobs
bash crontab -eAdd:plaintext 0 3 * * * rsync -av --delete /source/ /mnt/archive/This runs the backup every night at 3 AM.Automate Index Updates
bash 0 4 * * * find /mnt/archive > ~/Indexes/master_index.txt
So Making These Considerations
✔ Be Consistent – Maintain a structured system.
✔ Test Your Backups – Ensure archives are not corrupted before deleting originals.
✔ Plan for Growth – Maintain an efficient catalog as data expands.For data hoarders seeking reliable 2TB storage solutions and appropriate physical storage containers, here's a comprehensive overview:
2TB Storage Options
1. Hard Disk Drives (HDDs):
-
Western Digital My Book Series: These external HDDs are designed to resemble a standard black hardback book. They come in various editions, such as Essential, Premium, and Studio, catering to different user needs. citeturn0search19
-
Seagate Barracuda Series: Known for affordability and performance, these HDDs are suitable for general usage, including data hoarding. They offer storage capacities ranging from 500GB to 8TB, with speeds up to 190MB/s. citeturn0search20
2. Solid State Drives (SSDs):
- Seagate Barracuda SSDs: These SSDs come with either SATA or NVMe interfaces, storage sizes from 240GB to 2TB, and read speeds up to 560MB/s for SATA and 3,400MB/s for NVMe. They are ideal for faster data access and reliability. citeturn0search20
3. Network Attached Storage (NAS) Drives:
- Seagate IronWolf Series: Designed for NAS devices, these drives offer HDD storage capacities from 1TB to 20TB and SSD capacities from 240GB to 4TB. They are optimized for multi-user environments and continuous operation. citeturn0search20
Physical Storage Containers for 2TB Drives
Proper storage of your drives is crucial to ensure data integrity and longevity. Here are some recommendations:
1. Anti-Static Bags:
Essential for protecting drives from electrostatic discharge, especially during handling and transportation.
2. Protective Cases:
- Hard Drive Carrying Cases: These cases offer padded compartments to securely hold individual drives, protecting them from physical shocks and environmental factors.
3. Storage Boxes:
- Anti-Static Storage Boxes: Designed to hold multiple drives, these boxes provide organized storage with anti-static protection, ideal for archiving purposes.
4. Drive Caddies and Enclosures:
- HDD/SSD Enclosures: These allow internal drives to function as external drives, offering both protection and versatility in connectivity.
5. Fireproof and Waterproof Safes:
For long-term storage, consider safes that protect against environmental hazards, ensuring data preservation even in adverse conditions.
Storage Tips:
-
Labeling: Clearly label each drive with its contents and date of storage for easy identification.
-
Climate Control: Store drives in a cool, dry environment to prevent data degradation over time.
By selecting appropriate 2TB storage solutions and ensuring they are stored in suitable containers, you can effectively manage and protect your data hoard.
Here’s a set of custom Bash scripts to automate your archival workflow on Linux:
1️⃣ Compression & Archiving Script
This script compresses and archives files, organizing them by date.
```bash!/bin/bash
Compress and archive files into dated folders
ARCHIVE_DIR="/mnt/backup" DATE=$(date +"%Y-%m-%d") BACKUP_DIR="$ARCHIVE_DIR/$DATE"
mkdir -p "$BACKUP_DIR"
Find and compress files
find ~/Documents -type f -mtime -7 -print0 | tar --null -czvf "$BACKUP_DIR/archive.tar.gz" --files-from -
echo "Backup completed: $BACKUP_DIR/archive.tar.gz" ```
2️⃣ Indexing Script
This script creates a list of all archived files and saves it for easy lookup.
```bash!/bin/bash
Generate an index file for all backups
ARCHIVE_DIR="/mnt/backup" INDEX_FILE="$ARCHIVE_DIR/index.txt"
find "$ARCHIVE_DIR" -type f -name "*.tar.gz" > "$INDEX_FILE"
echo "Index file updated: $INDEX_FILE" ```
3️⃣ Storage Space Monitor
This script alerts you if the disk usage exceeds 90%.
```bash!/bin/bash
Monitor storage usage
THRESHOLD=90 USAGE=$(df -h | grep '/mnt/backup' | awk '{print $5}' | sed 's/%//')
if [ "$USAGE" -gt "$THRESHOLD" ]; then echo "WARNING: Disk usage at $USAGE%!" fi ```
4️⃣ Automatic HDD Swap Alert
This script checks if a new 2TB drive is connected and notifies you.
```bash!/bin/bash
Detect new drives and notify
WATCHED_SIZE="2T" DEVICE=$(lsblk -dn -o NAME,SIZE | grep "$WATCHED_SIZE" | awk '{print $1}')
if [ -n "$DEVICE" ]; then echo "New 2TB drive detected: /dev/$DEVICE" fi ```
5️⃣ Symbolic Link Organizer
This script creates symlinks to easily access archived files from a single directory.
```bash!/bin/bash
Organize files using symbolic links
ARCHIVE_DIR="/mnt/backup" LINK_DIR="$HOME/Archive_Links"
mkdir -p "$LINK_DIR" ln -s "$ARCHIVE_DIR"//.tar.gz "$LINK_DIR/"
echo "Symbolic links updated in $LINK_DIR" ```
🔥 How to Use These Scripts:
- Save each script as a
.shfile. - Make them executable using:
bash chmod +x script_name.sh - Run manually or set up a cron job for automation:
bash crontab -e
Add this line to run the backup every Sunday at midnight:
bash 0 0 * * 0 /path/to/backup_script.sh
Here's a Bash script to encrypt your backups using GPG (GnuPG) for strong encryption. 🚀
🔐 Backup & Encrypt Script
This script will:
✅ Compress files into an archive
✅ Encrypt it using GPG
✅ Store it in a secure location```bash
!/bin/bash
Backup and encrypt script
ARCHIVE_DIR="/mnt/backup" DATE=$(date +"%Y-%m-%d") BACKUP_FILE="$ARCHIVE_DIR/backup_$DATE.tar.gz" ENCRYPTED_FILE="$BACKUP_FILE.gpg" GPG_RECIPIENT="your@email.com" # Change this to your GPG key or use --symmetric for password-based encryption
mkdir -p "$ARCHIVE_DIR"
Compress files
tar -czvf "$BACKUP_FILE" ~/Documents
Encrypt the backup using GPG
gpg --output "$ENCRYPTED_FILE" --encrypt --recipient "$GPG_RECIPIENT" "$BACKUP_FILE"
Verify encryption success
if [ -f "$ENCRYPTED_FILE" ]; then echo "Backup encrypted successfully: $ENCRYPTED_FILE" rm "$BACKUP_FILE" # Remove unencrypted file for security else echo "Encryption failed!" fi ```
🔓 Decrypting a Backup
To restore a backup, run:
bash gpg --decrypt --output backup.tar.gz backup_YYYY-MM-DD.tar.gz.gpg tar -xzvf backup.tar.gz
🔁 Automating with Cron
To run this script every Sunday at midnight:
bash crontab -eAdd this line:
bash 0 0 * * 0 /path/to/encrypt_backup.sh
🔐 Backup & Encrypt Script (Password-Based)
This script:
✅ Compresses files into an archive
✅ Encrypts them using GPG with a passphrase
✅ Stores them in a secure location```bash
!/bin/bash
Backup and encrypt script (password-based)
ARCHIVE_DIR="/mnt/backup" DATE=$(date +"%Y-%m-%d") BACKUP_FILE="$ARCHIVE_DIR/backup_$DATE.tar.gz" ENCRYPTED_FILE="$BACKUP_FILE.gpg" PASSPHRASE="YourStrongPassphraseHere" # Change this!
mkdir -p "$ARCHIVE_DIR"
Compress files
tar -czvf "$BACKUP_FILE" ~/Documents
Encrypt the backup with a password
gpg --batch --yes --passphrase "$PASSPHRASE" --symmetric --cipher-algo AES256 --output "$ENCRYPTED_FILE" "$BACKUP_FILE"
Verify encryption success
if [ -f "$ENCRYPTED_FILE" ]; then echo "Backup encrypted successfully: $ENCRYPTED_FILE" rm "$BACKUP_FILE" # Remove unencrypted file for security else echo "Encryption failed!" fi ```
🔓 Decrypting a Backup
To restore a backup, run:
bash gpg --batch --yes --passphrase "YourStrongPassphraseHere" --decrypt --output backup.tar.gz backup_YYYY-MM-DD.tar.gz.gpg tar -xzvf backup.tar.gz
🔁 Automating with Cron
To run this script every Sunday at midnight:
bash crontab -eAdd this line:
bash 0 0 * * 0 /path/to/encrypt_backup.sh
🔥 Security Best Practices
- Do NOT hardcode the password in the script. Instead, store it in a secure location like a
.gpg-passfile and use:
bash PASSPHRASE=$(cat /path/to/.gpg-pass) - Use a strong passphrase with at least 16+ characters.
- Consider using a hardware security key or YubiKey for extra security.
Here's how you can add automatic cloud syncing to your encrypted backups. This script will sync your encrypted backups to a cloud storage service like Rsync, Dropbox, or Nextcloud using the rclone tool, which is compatible with many cloud providers.
Step 1: Install rclone
First, you need to install
rcloneif you haven't already. It’s a powerful tool for managing cloud storage.-
Install rclone:
bash curl https://rclone.org/install.sh | sudo bash -
Configure rclone with your cloud provider (e.g., Google Drive):
bash rclone config
Follow the prompts to set up your cloud provider. After configuration, you'll have a "remote" (e.g.,
rsyncfor https://rsync.net) to use in the script.
🔐 Backup, Encrypt, and Sync to Cloud Script
This script will: ✅ Compress files into an archive
✅ Encrypt them with a password
✅ Sync the encrypted backup to the cloud storage```bash
!/bin/bash
Backup, encrypt, and sync to cloud script (password-based)
ARCHIVE_DIR="/mnt/backup" DATE=$(date +"%Y-%m-%d") BACKUP_FILE="$ARCHIVE_DIR/backup_$DATE.tar.gz" ENCRYPTED_FILE="$BACKUP_FILE.gpg" PASSPHRASE="YourStrongPassphraseHere" # Change this!
Cloud configuration (rclone remote name)
CLOUD_REMOTE="gdrive" # Change this to your remote name (e.g., 'gdrive', 'dropbox', 'nextcloud') CLOUD_DIR="backups" # Cloud directory where backups will be stored
mkdir -p "$ARCHIVE_DIR"
Compress files
tar -czvf "$BACKUP_FILE" ~/Documents
Encrypt the backup with a password
gpg --batch --yes --passphrase "$PASSPHRASE" --symmetric --cipher-algo AES256 --output "$ENCRYPTED_FILE" "$BACKUP_FILE"
Verify encryption success
if [ -f "$ENCRYPTED_FILE" ]; then echo "Backup encrypted successfully: $ENCRYPTED_FILE" rm "$BACKUP_FILE" # Remove unencrypted file for security
# Sync the encrypted backup to the cloud using rclone rclone copy "$ENCRYPTED_FILE" "$CLOUD_REMOTE:$CLOUD_DIR" --progress # Verify sync success if [ $? -eq 0 ]; then echo "Backup successfully synced to cloud: $CLOUD_REMOTE:$CLOUD_DIR" rm "$ENCRYPTED_FILE" # Remove local backup after syncing else echo "Cloud sync failed!" fielse echo "Encryption failed!" fi ```
How to Use the Script:
- Edit the script:
- Change the
PASSPHRASEto a secure passphrase. - Change
CLOUD_REMOTEto your cloud provider’s rclone remote name (e.g.,gdrive,dropbox). -
Change
CLOUD_DIRto the cloud folder where you'd like to store the backup. -
Set up a cron job for automatic backups:
- To run the backup every Sunday at midnight, add this line to your crontab:
bash crontab -eAdd:
bash 0 0 * * 0 /path/to/backup_encrypt_sync.sh
🔥 Security Tips:
- Store the passphrase securely (e.g., use a
.gpg-passfile withcat /path/to/.gpg-pass). - Use rclone's encryption feature for sensitive data in the cloud if you want to encrypt before uploading.
- Use multiple cloud services (e.g., Google Drive and Dropbox) for redundancy.
📌 START → **Planning Your Data Archiving Strategy**├── What type of data? (Docs, Media, Code, etc.)
├── How often will you need access? (Daily, Monthly, Rarely)
├── Choose storage type: SSD (fast), HDD (cheap), Tape (long-term)
├── Plan directory structure (YYYY-MM-DD, Category-Based, etc.)
└── Define retention policy (Keep Forever? Auto-Delete After X Years?)
↓📌 Choosing the Right Storage & Filesystem
├── Local storage: (ext4, XFS, Btrfs, ZFS for snapshots)
├── Network storage: (NAS, Nextcloud, Syncthing)
├── Cold storage: (M-DISC, Tape Backup, External HDD)
├── Redundancy: (RAID, SnapRAID, ZFS Mirror, Cloud Sync)
└── Encryption: (LUKS, VeraCrypt, age, gocryptfs)
↓📌 Organizing & Indexing Data
├── Folder structure: (YYYY/MM/Project-Based)
├── Metadata tagging: (exiftool, Recoll, TagSpaces)
├── Search tools: (fd, fzf, locate, grep)
├── Deduplication: (rdfind, fdupes, hardlinking)
└── Checksum integrity: (sha256sum, blake3)
↓📌 Compression & Space Optimization
├── Use compression (tar, zip, 7z, zstd, btrfs/zfs compression)
├── Remove duplicate files (rsync, fdupes, rdfind)
├── Store archives in efficient formats (ISO, SquashFS, borg)
├── Use incremental backups (rsync, BorgBackup, Restic)
└── Verify archive integrity (sha256sum, snapraid sync)
↓📌 Ensuring Long-Term Data Integrity
├── Check data periodically (snapraid scrub, btrfs scrub)
├── Refresh storage media every 3-5 years (HDD, Tape)
├── Protect against bit rot (ZFS/Btrfs checksums, ECC RAM)
├── Store backup keys & logs separately (Paper, YubiKey, Trezor)
└── Use redundant backups (3-2-1 Rule: 3 copies, 2 locations, 1 offsite)
↓📌 Accessing Data Efficiently
├── Use symbolic links & bind mounts for easy access
├── Implement full-text search (Recoll, Apache Solr, Meilisearch)
├── Set up a file index database (mlocate, updatedb)
├── Utilize file previews (nnn, ranger, vifm)
└── Configure network file access (SFTP, NFS, Samba, WebDAV)
↓📌 Scaling & Expanding Your Archive
├── Move old data to slower storage (HDD, Tape, Cloud)
├── Upgrade storage (LVM expansion, RAID, NAS upgrades)
├── Automate archival processes (cron jobs, systemd timers)
├── Optimize backups for large datasets (rsync --link-dest, BorgBackup)
└── Add redundancy as data grows (RAID, additional HDDs)
↓📌 Automating the Archival Process
├── Schedule regular backups (cron, systemd, Ansible)
├── Auto-sync to offsite storage (rclone, Syncthing, Nextcloud)
├── Monitor storage health (smartctl, btrfs/ZFS scrub, netdata)
├── Set up alerts for disk failures (Zabbix, Grafana, Prometheus)
└── Log & review archive activity (auditd, logrotate, shell scripts)
↓✅ GOAT STATUS: DATA ARCHIVING COMPLETE & AUTOMATED! 🎯
-
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ d34e832d:383f78d0
2025-03-07 00:05:12
@ d34e832d:383f78d0
2025-03-07 00:05:12Writer: H. G. Wells English Short stories Fiction Speculative fiction Science fiction Apocalyptic Dystopian Dying Earth Science fantasy 1895 British Originally published in magazines Set in Surrey Social science fiction Time travel Veganism
The Time Traveller (for so it will be convenient to speak of him) was expounding a recondite matter to us. His grey eyes shone and twinkled, and his usually pale face was flushed and animated. The fire burned brightly, and the soft radiance of the incandescent lights in the lilies of silver caught the bubbles that flashed and passed in our glasses. Our chairs, being his patents, embraced and caressed us rather than submitted to be sat upon, and there was that luxurious after-dinner atmosphere when thought roams gracefully free of the trammels of precision. And he put it to us in this way–marking the points with a lean forefinger–as we sat and lazily admired his earnestness over this new paradox (as we thought it:) and his fecundity.
`You must follow me carefully. I shall have to controvert one or two ideas that are almost universally accepted. The geometry, for instance, they taught you at school is founded on a misconception.’
`Is not that rather a large thing to expect us to begin upon?’ said Filby, an argumentative person with red hair.
`I do not mean to ask you to accept anything without reasonable ground for it. You will soon admit as much as I need from you. You know of course that a mathematical line, a line of thickness NIL, has no real existence. They taught you that? Neither has a mathematical plane. These things are mere abstractions.’
`That is all right,’ said the Psychologist.
`Nor, having only length, breadth, and thickness, can a cube have a real existence.’
There I object,’ said Filby.Of course a solid body may exist. All real things–‘`So most people think. But wait a moment. Can an INSTANTANEOUS cube exist?’
`Don’t follow you,’ said Filby.
`Can a cube that does not last for any time at all, have a real existence?’
Filby became pensive.
Clearly,’ the Time Traveller proceeded,any real body must have extension in FOUR directions: it must have Length, Breadth, Thickness, and–Duration. But through a natural infirmity of the flesh, which I will explain to you in a moment, we incline to overlook this fact. There are really four dimensions, three which we call the three planes of Space, and a fourth, Time. There is, however, a tendency to draw an unreal distinction between the former three dimensions and the latter, because it happens that our consciousness moves intermittently in one direction along the latter from the beginning to the end of our lives.’That,’ said a very young man, making spasmodic efforts to relight his cigar over the lamp;that . . . very clear indeed.’Now, it is very remarkable that this is so extensively overlooked,’ continued the Time Traveller, with a slight accession of cheerfulness.Really this is what is meant by the Fourth Dimension, though some people who talk about the Fourth Dimension do not know they mean it. It is only another way of looking at Time. THERE IS NO DIFFERENCE BETWEEN TIME AND ANY OF THE THREE DIMENSIONS OF SPACE EXCEPT THAT OUR CONSCIOUSNESS MOVES ALONG IT. But some foolish people have got hold of the wrong side of that idea. You have all heard what they have to say about this Fourth Dimension?’`I have not,’ said the Provincial Mayor.
`It is simply this. That Space, as our mathematicians have it, is spoken of as having three dimensions, which one may call Length, Breadth, and Thickness, and is always definable by reference to three planes, each at right angles to the others. But some philosophical people have been asking why THREE dimensions particularly–why not another direction at right angles to the other three?–and have even tried to construct a Four-Dimension geometry. Professor Simon Newcomb was expounding this to the New York Mathematical Society only a month or so ago. You know how on a flat surface, which has only two dimensions, we can represent a figure of a three-dimensional solid, and similarly they think that by models of thee dimensions they could represent one of four–if they could master the perspective of the thing. See?’
I think so,’ murmured the Provincial Mayor; and, knitting his brows, he lapsed into an introspective state, his lips moving as one who repeats mystic words.Yes, I think I see it now,’ he said after some time, brightening in a quite transitory manner.`Well, I do not mind telling you I have been at work upon this geometry of Four Dimensions for some time. Some of my results are curious. For instance, here is a portrait of a man at eight years old, another at fifteen, another at seventeen, another at twenty-three, and so on. All these are evidently sections, as it were, Three-Dimensional representations of his Four-Dimensioned being, which is a fixed and unalterable thing.
Scientific people,’ proceeded the Time Traveller, after the pause required for the proper assimilation of this,know very well that Time is only a kind of Space. Here is a popular scientific diagram, a weather record. This line I trace with my finger shows the movement of the barometer. Yesterday it was so high, yesterday night it fell, then this morning it rose again, and so gently upward to here. Surely the mercury did not trace this line in any of the dimensions of Space generally recognized? But certainly it traced such a line, and that line, therefore, we must conclude was along the Time-Dimension.’But,’ said the Medical Man, staring hard at a coal in the fire,if Time is really only a fourth dimension of Space, why is it, and why has it always been, regarded as something different? And why cannot we move in Time as we move about in the other dimensions of Space?’The Time Traveller smiled. `Are you sure we can move freely in Space? Right and left we can go, backward and forward freely enough, and men always have done so. I admit we move freely in two dimensions. But how about up and down? Gravitation limits us there.’
Not exactly,’ said the Medical Man.There are balloons.’But before the balloons, save for spasmodic jumping and the inequalities of the surface, man had no freedom of vertical movement.’Still they could move a little up and down,’ said the Medical Man.`Easier, far easier down than up.’
`And you cannot move at all in Time, you cannot get away from the present moment.’
`My dear sir, that is just where you are wrong. That is just where the whole world has gone wrong. We are always getting away from the present moment. Our mental existences, which are immaterial and have no dimensions, are passing along the Time-Dimension with a uniform velocity from the cradle to the grave. Just as we should travel DOWN if we began our existence fifty miles above the earth’s surface.’
But the great difficulty is this,’ interrupted the Psychologist.You CAN move about in all directions of Space, but you cannot move about in Time.’`That is the germ of my great discovery. But you are wrong to say that we cannot move about in Time. For instance, if I am recalling an incident very vividly I go back to the instant of its occurrence: I become absent-minded, as you say. I jump back for a moment. Of course we have no means of staying back for any length of Time, any more than a savage or an animal has of staying six feet above the ground. But a civilized man is better off than the savage in this respect. He can go up against gravitation in a balloon, and why should he not hope that ultimately he may be able to stop or accelerate his drift along the Time-Dimension, or even turn about and travel the other way?’
Oh, THIS,’ began Filby,is all–‘`Why not?’ said the Time Traveller.
`It’s against reason,’ said Filby.
`What reason?’ said the Time Traveller.
You can show black is white by argument,’ said Filby,but you will never convince me.’Possibly not,’ said the Time Traveller.But now you begin to see the object of my investigations into the geometry of Four Dimensions. Long ago I had a vague inkling of a machine–‘`To travel through Time!’ exclaimed the Very Young Man.
`That shall travel indifferently in any direction of Space and Time, as the driver determines.’
Filby contented himself with laughter.
`But I have experimental verification,’ said the Time Traveller.
It would be remarkably convenient for the historian,’ the Psychologist suggested.One might travel back and verify the accepted account of the Battle of Hastings, for instance!’Don’t you think you would attract attention?’ said the Medical Man.Our ancestors had no great tolerance for anachronisms.’`One might get one’s Greek from the very lips of Homer and Plato,’ the Very Young Man thought.
`In which case they would certainly plough you for the Little-go. The German scholars have improved Greek so much.’
Then there is the future,’ said the Very Young Man.Just think! One might invest all one’s money, leave it to accumulate at interest, and hurry on ahead!’To discover a society,’ said I,erected on a strictly communistic basis.’`Of all the wild extravagant theories!’ began the Psychologist.
`Yes, so it seemed to me, and so I never talked of it until–‘
Experimental verification!’ cried I.You are going to verify THAT?’`The experiment!’ cried Filby, who was getting brain-weary.
Let’s see your experiment anyhow,’ said the Psychologist,though it’s all humbug, you know.’The Time Traveller smiled round at us. Then, still smiling faintly, and with his hands deep in his trousers pockets, he walked slowly out of the room, and we heard his slippers shuffling down the long passage to his laboratory.
The Psychologist looked at us. `I wonder what he’s got?’
`Some sleight-of-hand trick or other,’ said the Medical Man, and Filby tried to tell us about a conjurer he had seen at Burslem; but before he had finished his preface the Time Traveller came back, and Filby’s anecdote collapsed.
The thing the Time Traveller held in his hand was a glittering metallic framework, scarcely larger than a small clock, and very delicately made. There was ivory in it, and some transparent crystalline substance. And now I must be explicit, for this that follows–unless his explanation is to be accepted–is an absolutely unaccountable thing. He took one of the small octagonal tables that were scattered about the room, and set it in front of the fire, with two legs on the hearthrug. On this table he placed the mechanism. Then he drew up a chair, and sat down. The only other object on the table was a small shaded lamp, the bright light of which fell upon the model. There were also perhaps a dozen candles about, two in brass candlesticks upon the mantel and several in sconces, so that the room was brilliantly illuminated. I sat in a low arm-chair nearest the fire, and I drew this forward so as to be almost between the Time Traveller and the fireplace. Filby sat behind him, looking over his shoulder. The Medical Man and the Provincial Mayor watched him in profile from the right, the Psychologist from the left. The Very Young Man stood behind the Psychologist. We were all on the alert. It appears incredible to me that any kind of trick, however subtly conceived and however adroitly done, could have been played upon us under these conditions.
The Time Traveller looked at us, and then at the mechanism. `Well?’ said the Psychologist.
This little affair,’ said the Time Traveller, resting his elbows upon the table and pressing his hands together above the apparatus,is only a model. It is my plan for a machine to travel through time. You will notice that it looks singularly askew, and that there is an odd twinkling appearance about this bar, as though it was in some way unreal.’ He pointed to the part with his finger. `Also, here is one little white lever, and here is another.’The Medical Man got up out of his chair and peered into the thing. `It’s beautifully made,’ he said.
It took two years to make,’ retorted the Time Traveller. Then, when we had all imitated the action of the Medical Man, he said:Now I want you clearly to understand that this lever, being pressed over, sends the machine gliding into the future, and this other reverses the motion. This saddle represents the seat of a time traveller. Presently I am going to press the lever, and off the machine will go. It will vanish, pass into future Time, and disappear. Have a good look at the thing. Look at the table too, and satisfy yourselves there is no trickery. I don’t want to waste this model, and then be told I’m a quack.’There was a minute’s pause perhaps. The Psychologist seemed about to speak to me, but changed his mind. Then the Time Traveller put forth his finger towards the lever.
No,’ he said suddenly.Lend me your hand.’ And turning to the Psychologist, he took that individual’s hand in his own and told him to put out his forefinger. So that it was the Psychologist himself who sent forth the model Time Machine on its interminable voyage. We all saw the lever turn. I am absolutely certain there was no trickery. There was a breath of wind, and the lamp flame jumped. One of the candles on the mantel was blown out, and the little machine suddenly swung round, became indistinct, was seen as a ghost for a second perhaps, as an eddy of faintly glittering brass and ivory; and it was gone–vanished! Save for the lamp the table was bare.Everyone was silent for a minute. Then Filby said he was damned.
The Psychologist recovered from his stupor, and suddenly looked under the table. At that the Time Traveller laughed cheerfully. `Well?’ he said, with a reminiscence of the Psychologist. Then, getting up, he went to the tobacco jar on the mantel, and with his back to us began to fill his pipe.
We stared at each other.
Look here,’ said the Medical Man,are you in earnest about this? Do you seriously believe that that machine has travelled into time?’Certainly,’ said the Time Traveller, stooping to light a spill at the fire. Then he turned, lighting his pipe, to look at the Psychologist’s face. (The Psychologist, to show that he was not unhinged, helped himself to a cigar and tried to light it uncut.)What is more, I have a big machine nearly finished in there’–he indicated the laboratory–`and when that is put together I mean to have a journey on my own account.’`You mean to say that that machine has travelled into the future?’ said Filby.
`Into the future or the past–I don’t, for certain, know which.’
After an interval the Psychologist had an inspiration. `It must have gone into the past if it has gone anywhere,’ he said.
`Why?’ said the Time Traveller.
`Because I presume that it has not moved in space, and if it travelled into the future it would still be here all this time, since it must have travelled through this time.’
But,’ I said,If it travelled into the past it would have been visible when we came first into this room; and last Thursday when we were here; and the Thursday before that; and so forth!’`Serious objections,’ remarked the Provincial Mayor, with an air of impartiality, turning towards the Time Traveller.
Not a bit,’ said the Time Traveller, and, to the Psychologist:You think. You can explain that. It’s presentation below the threshold, you know, diluted presentation.’Of course,’ said the Psychologist, and reassured us.That’s a simple point of psychology. I should have thought of it. It’s plain enough, and helps the paradox delightfully. We cannot see it, nor can we appreciate this machine, any more than we can the spoke of a wheel spinning, or a bullet flying through the air. If it is travelling through time fifty times or a hundred times faster than we are, if it gets through a minute while we get through a second, the impression it creates will of course be only one-fiftieth or one-hundredth of what it would make if it were not travelling in time. That’s plain enough.’ He passed his hand through the space in which the machine had been. `You see?’ he said, laughing.We sat and stared at the vacant table for a minute or so. Then the Time Traveller asked us what we thought of it all.
`It sounds plausible enough to-night,’ said the Medical Man; ‘but wait until to-morrow. Wait for the common sense of the morning.’
`Would you like to see the Time Machine itself?’ asked the Time Traveller. And therewith, taking the lamp in his hand, he led the way down the long, draughty corridor to his laboratory. I remember vividly the flickering light, his queer, broad head in silhouette, the dance of the shadows, how we all followed him, puzzled but incredulous, and how there in the laboratory we beheld a larger edition of the little mechanism which we had seen vanish from before our eyes. Parts were of nickel, parts of ivory, parts had certainly been filed or sawn out of rock crystal. The thing was generally complete, but the twisted crystalline bars lay unfinished upon the bench beside some sheets of drawings, and I took one up for a better look at it. Quartz it seemed to be.
Look here,’ said the Medical Man,are you perfectly serious? Or is this a trick–like that ghost you showed us last Christmas?’Upon that machine,’ said the Time Traveller, holding the lamp aloft,I intend to explore time. Is that plain? I was never more serious in my life.’None of us quite knew how to take it.
I caught Filby’s eye over the shoulder of the Medical Man, and he winked at me solemnly.
II
I think that at that time none of us quite believed in the Time Machine. The fact is, the Time Traveller was one of those men who are too clever to be believed: you never felt that you saw all round him; you always suspected some subtle reserve, some ingenuity in ambush, behind his lucid frankness. Had Filby shown the model and explained the matter in the Time Traveller’s words, we should have shown HIM far less scepticism. For we should have perceived his motives; a pork butcher could understand Filby. But the Time Traveller had more than a touch of whim among his elements, and we distrusted him. Things that would have made the frame of a less clever man seemed tricks in his hands. It is a mistake to do things too easily. The serious people who took him seriously never felt quite sure of his deportment; they were somehow aware that trusting their reputations for judgment with him was like furnishing a nursery with egg-shell china. So I don’t think any of us said very much about time travelling in the interval between that Thursday and the next, though its odd potentialities ran, no doubt, in most of our minds: its plausibility, that is, its practical incredibleness, the curious possibilities of anachronism and of utter confusion it suggested. For my own part, I was particularly preoccupied with the trick of the model. That I remember discussing with the Medical Man, whom I met on Friday at the Linnaean. He said he had seen a similar thing at Tubingen, and laid considerable stress on the blowing out of the candle. But how the trick was done he could not explain.
The next Thursday I went again to Richmond–I suppose I was one of the Time Traveller’s most constant guests–and, arriving late, found four or five men already assembled in his drawing-room. The Medical Man was standing before the fire with a sheet of paper in one hand and his watch in the other. I looked round for the Time Traveller, and–
It’s half-past seven now,’ said the Medical Man.I suppose we’d better have dinner?’`Where’s—-?’ said I, naming our host.
`You’ve just come? It’s rather odd. He’s unavoidably detained. He asks me in this note to lead off with dinner at seven if he’s not back. Says he’ll explain when he comes.’
`It seems a pity to let the dinner spoil,’ said the Editor of a well-known daily paper; and thereupon the Doctor rang the bell.
The Psychologist was the only person besides the Doctor and myself who had attended the previous dinner. The other men were Blank, the Editor aforementioned, a certain journalist, and another–a quiet, shy man with a beard–whom I didn’t know, and who, as far as my observation went, never opened his mouth all the evening. There was some speculation at the dinner-table about the Time Traveller’s absence, and I suggested time travelling, in a half-jocular spirit. The Editor wanted that explained to him, and the Psychologist volunteered a wooden account of the
ingenious paradox and trick’ we had witnessed that day week. He was in the midst of his exposition when the door from the corridor opened slowly and without noise. I was facing the door, and saw it first.Hallo!’ I said.At last!’ And the door opened wider, and the Time Traveller stood before us. I gave a cry of surprise.Good heavens! man, what’s the matter?’ cried the Medical Man, who saw him next. And the whole tableful turned towards the door.He was in an amazing plight. His coat was dusty and dirty, and smeared with green down the sleeves; his hair disordered, and as it seemed to me greyer–either with dust and dirt or because its colour had actually faded. His face was ghastly pale; his chin had a brown cut on it–a cut half healed; his expression was haggard and drawn, as by intense suffering. For a moment he hesitated in the doorway, as if he had been dazzled by the light. Then he came into the room. He walked with just such a limp as I have seen in footsore tramps. We stared at him in silence, expecting him to speak.
He said not a word, but came painfully to the table, and made a motion towards the wine. The Editor filled a glass of champagne, and pushed it towards him. He drained it, and it seemed to do him good: for he looked round the table, and the ghost of his old smile flickered across his face.
What on earth have you been up to, man?’ said the Doctor. The Time Traveller did not seem to hear.Don’t let me disturb you,’ he said, with a certain faltering articulation.I’m all right.’ He stopped, held out his glass for more, and took it off at a draught.That’s good,’ he said. His eyes grew brighter, and a faint colour came into his cheeks. His glance flickered over our faces with a certain dull approval, and then went round the warm and comfortable room. Then he spoke again, still as it were feeling his way among his words. `I’m going to wash and dress, and then I’ll come down and explain things. . . Save me some of that mutton. I’m starving for a bit of meat.’He looked across at the Editor, who was a rare visitor, and hoped he was all right. The Editor began a question.
Tell you presently,’ said the Time Traveller.I’m–funny! Be all right in a minute.’He put down his glass, and walked towards the staircase door. Again I remarked his lameness and the soft padding sound of his footfall, and standing up in my place, I saw his feet as he went out. He had nothing on them but a pair of tattered blood-stained socks. Then the door closed upon him. I had half a mind to follow, till I remembered how he detested any fuss about himself. For a minute, perhaps, my mind was wool-gathering. Then, ‘Remarkable Behaviour of an Eminent Scientist,’ I heard the Editor say, thinking (after his wont) in headlines. And this brought my attention back to the bright dinner-table.
What’s the game?’ said the Journalist.Has he been doing the Amateur Cadger? I don’t follow.’ I met the eye of the Psychologist, and read my own interpretation in his face. I thought of the Time Traveller limping painfully upstairs. I don’t think any one else had noticed his lameness.The first to recover completely from this surprise was the Medical Man, who rang the bell–the Time Traveller hated to have servants waiting at dinner–for a hot plate. At that the Editor turned to his knife and fork with a grunt, and the Silent Man followed suit. The dinner was resumed. Conversation was exclamatory for a little while, with gaps of wonderment; and then the Editor got fervent in his curiosity.
Does our friend eke out his modest income with a crossing? or has he his Nebuchadnezzar phases?’ he inquired.I feel assured it’s this business of the Time Machine,’ I said, and took up the Psychologist’s account of our previous meeting. The new guests were frankly incredulous. The Editor raised objections.What WAS this time travelling? A man couldn’t cover himself with dust by rolling in a paradox, could he?’ And then, as the idea came home to him, he resorted to caricature. Hadn’t they any clothes-brushes in the Future? The Journalist too, would not believe at any price, and joined the Editor in the easy work of heaping ridicule on the whole thing. They were both the new kind of journalist–very joyous, irreverent young men.Our Special Correspondent in the Day after To-morrow reports,’ the Journalist was saying–or rather shouting–when the Time Traveller came back. He was dressed in ordinary evening clothes, and nothing save his haggard look remained of the change that had startled me.I say,’ said the Editor hilariously,these chaps here say you have been travelling into the middle of next week! Tell us all about little Rosebery, will you? What will you take for the lot?’The Time Traveller came to the place reserved for him without a word. He smiled quietly, in his old way.
Where’s my mutton?’ he said.What a treat it is to stick a fork into meat again!’`Story!’ cried the Editor.
Story be damned!’ said the Time Traveller.I want something to eat. I won’t say a word until I get some peptone into my arteries. Thanks. And the salt.’One word,’ said I.Have you been time travelling?’`Yes,’ said the Time Traveller, with his mouth full, nodding his head.
I’d give a shilling a line for a verbatim note,’ said the Editor. The Time Traveller pushed his glass towards the Silent Man and rang it with his fingernail; at which the Silent Man, who had been staring at his face, started convulsively, and poured him wine. The rest of the dinner was uncomfortable. For my own part, sudden questions kept on rising to my lips, and I dare say it was the same with the others. The Journalist tried to relieve the tension by telling anecdotes of Hettie Potter. The Time Traveller devoted his attention to his dinner, and displayed the appetite of a tramp. The Medical Man smoked a cigarette, and watched the Time Traveller through his eyelashes. The Silent Man seemed even more clumsy than usual, and drank champagne with regularity and determination out of sheer nervousness. At last the Time Traveller pushed his plate away, and looked round us.I suppose I must apologize,’ he said.I was simply starving. I’ve had a most amazing time.’ He reached out his hand for a cigar, and cut the end.But come into the smoking-room. It’s too long a story to tell over greasy plates.’ And ringing the bell in passing, he led the way into the adjoining room.`You have told Blank, and Dash, and Chose about the machine?’ he said to me, leaning back in his easy-chair and naming the three new guests.
`But the thing’s a mere paradox,’ said the Editor.
I can’t argue to-night. I don’t mind telling you the story, but I can’t argue. I will,’ he went on,tell you the story of what has happened to me, if you like, but you must refrain from interruptions. I want to tell it. Badly. Most of it will sound like lying. So be it! It’s true–every word of it, all the same. I was in my laboratory at four o’clock, and since then . . . I’ve lived eight days . . . such days as no human being ever lived before! I’m nearly worn out, but I shan’t sleep till I’ve told this thing over to you. Then I shall go to bed. But no interruptions! Is it agreed?’Agreed,’ said the Editor, and the rest of us echoedAgreed.’ And with that the Time Traveller began his story as I have set it forth. He sat back in his chair at first, and spoke like a weary man. Afterwards he got more animated. In writing it down I feel with only too much keenness the inadequacy of pen and ink –and, above all, my own inadequacy–to express its quality. You read, I will suppose, attentively enough; but you cannot see the speaker’s white, sincere face in the bright circle of the little lamp, nor hear the intonation of his voice. You cannot know how his expression followed the turns of his story! Most of us hearers were in shadow, for the candles in the smoking-room had not been lighted, and only the face of the Journalist and the legs of the Silent Man from the knees downward were illuminated. At first we glanced now and again at each other. After a time we ceased to do that, and looked only at the Time Traveller’s face.III
`I told some of you last Thursday of the principles of the Time Machine, and showed you the actual thing itself, incomplete in the workshop. There it is now, a little travel-worn, truly; and one of the ivory bars is cracked, and a brass rail bent; but the rest of it’s sound enough. I expected to finish it on Friday, but on Friday, when the putting together was nearly done, I found that one of the nickel bars was exactly one inch too short, and this I had to get remade; so that the thing was not complete until this morning. It was at ten o’clock to-day that the first of all Time Machines began its career. I gave it a last tap, tried all the screws again, put one more drop of oil on the quartz rod, and sat myself in the saddle. I suppose a suicide who holds a pistol to his skull feels much the same wonder at what will come next as I felt then. I took the starting lever in one hand and the stopping one in the other, pressed the first, and almost immediately the second. I seemed to reel; I felt a nightmare sensation of falling; and, looking round, I saw the laboratory exactly as before. Had anything happened? For a moment I suspected that my intellect had tricked me. Then I noted the clock. A moment before, as it seemed, it had stood at a minute or so past ten; now it was nearly half-past three!
`I drew a breath, set my teeth, gripped the starting lever with both hands, and went off with a thud. The laboratory got hazy and went dark. Mrs. Watchett came in and walked, apparently without seeing me, towards the garden door. I suppose it took her a minute or so to traverse the place, but to me she seemed to shoot across the room like a rocket. I pressed the lever over to its extreme position. The night came like the turning out of a lamp, and in another moment came to-morrow. The laboratory grew faint and hazy, then fainter and ever fainter. To-morrow night came black, then day again, night again, day again, faster and faster still. An eddying murmur filled my ears, and a strange, dumb confusedness descended on my mind.
`I am afraid I cannot convey the peculiar sensations of time travelling. They are excessively unpleasant. There is a feeling exactly like that one has upon a switchback–of a helpless headlong motion! I felt the same horrible anticipation, too, of an imminent smash. As I put on pace, night followed day like the flapping of a black wing. The dim suggestion of the laboratory seemed presently to fall away from me, and I saw the sun hopping swiftly across the sky, leaping it every minute, and every minute marking a day. I supposed the laboratory had been destroyed and I had come into the open air. I had a dim impression of scaffolding, but I was already going too fast to be conscious of any moving things. The slowest snail that ever crawled dashed by too fast for me. The twinkling succession of darkness and light was excessively painful to the eye. Then, in the intermittent darknesses, I saw the moon spinning swiftly through her quarters from new to full, and had a faint glimpse of the circling stars. Presently, as I went on, still gaining velocity, the palpitation of night and day merged into one continuous greyness; the sky took on a wonderful deepness of blue, a splendid luminous color like that of early twilight; the jerking sun became a streak of fire, a brilliant arch, in space; the moon a fainter fluctuating band; and I could see nothing of the stars, save now and then a brighter circle flickering in the blue.
`The landscape was misty and vague. I was still on the hill-side upon which this house now stands, and the shoulder rose above me grey and dim. I saw trees growing and changing like puffs of vapour, now brown, now green; they grew, spread, shivered, and passed away. I saw huge buildings rise up faint and fair, and pass like dreams. The whole surface of the earth seemed changed–melting and flowing under my eyes. The little hands upon the dials that registered my speed raced round faster and faster. Presently I noted that the sun belt swayed up and down, from solstice to solstice, in a minute or less, and that consequently my pace was over a year a minute; and minute by minute the white snow flashed across the world, and vanished, and was followed by the bright, brief green of spring.
`The unpleasant sensations of the start were less poignant now. They merged at last into a kind of hysterical exhilaration. I remarked indeed a clumsy swaying of the machine, for which I was unable to account. But my mind was too confused to attend to it, so with a kind of madness growing upon me, I flung myself into futurity. At first I scarce thought of stopping, scarce thought of anything but these new sensations. But presently a fresh series of impressions grew up in my mind–a certain curiosity and therewith a certain dread–until at last they took complete possession of me. What strange developments of humanity, what wonderful advances upon our rudimentary civilization, I thought, might not appear when I came to look nearly into the dim elusive world that raced and fluctuated before my eyes! I saw great and splendid architecture rising about me, more massive than any buildings of our own time, and yet, as it seemed, built of glimmer and mist. I saw a richer green flow up the hill-side, and remain there, without any wintry intermission. Even through the veil of my confusion the earth seemed very fair. And so my mind came round to the business of stopping,
`The peculiar risk lay in the possibility of my finding some substance in the space which I, or the machine, occupied. So long as I travelled at a high velocity through time, this scarcely mattered; I was, so to speak, attenuated–was slipping like a vapour through the interstices of intervening substances! But to come to a stop involved the jamming of myself, molecule by molecule, into whatever lay in my way; meant bringing my atoms into such intimate contact with those of the obstacle that a profound chemical reaction–possibly a far-reaching explosion –would result, and blow myself and my apparatus out of all possible dimensions–into the Unknown. This possibility had occurred to me again and again while I was making the machine; but then I had cheerfully accepted it as an unavoidable risk– one of the risks a man has got to take! Now the risk was inevitable, I no longer saw it in the same cheerful light. The fact is that insensibly, the absolute strangeness of everything, the sickly jarring and swaying of the machine, above all, the feeling of prolonged falling, had absolutely upset my nerve. I told myself that I could never stop, and with a gust of petulance I resolved to stop forthwith. Like an impatient fool, I lugged over the lever, and incontinently the thing went reeling over, and I was flung headlong through the air.
`There was the sound of a clap of thunder in my ears. I may have been stunned for a moment. A pitiless hail was hissing round me, and I was sitting on soft turf in front of the overset machine. Everything still seemed grey, but presently I remarked that the confusion in my ears was gone. I looked round me. I was on what seemed to be a little lawn in a garden, surrounded by rhododendron bushes, and I noticed that their mauve and purple blossoms were dropping in a shower under the beating of the hail-stones. The rebounding, dancing hail hung in a cloud over the machine, and drove along the ground like smoke. In a moment I was wet to the skin. “Fine hospitality,” said I, “to a man who has travelled innumerable years to see you.”
`Presently I thought what a fool I was to get wet. I stood up and looked round me. A colossal figure, carved apparently in some white stone, loomed indistinctly beyond the rhododendrons through the hazy downpour. But all else of the world was invisible.
`My sensations would be hard to describe. As the columns of hail grew thinner, I saw the white figure more distinctly. It was very large, for a silver birch-tree touched its shoulder. It was of white marble, in shape something like a winged sphinx, but the wings, instead of being carried vertically at the sides, were spread so that it seemed to hover. The pedestal, it appeared to me, was of bronze, and was thick with verdigris. It chanced that the face was towards me; the sightless eyes seemed to watch me; there was the faint shadow of a smile on the lips. It was greatly weather-worn, and that imparted an unpleasant suggestion of disease. I stood looking at it for a little space–half a minute, perhaps, or half an hour. It seemed to advance and to recede as the hail drove before it denser or thinner. At last I tore my eyes from it for a moment and saw that the hail curtain had worn threadbare, and that the sky was lightening with the promise of the Sun.
`I looked up again at the crouching white shape, and the full temerity of my voyage came suddenly upon me. What might appear when that hazy curtain was altogether withdrawn? What might not have happened to men? What if cruelty had grown into a common passion? What if in this interval the race had lost its manliness and had developed into something inhuman, unsympathetic, and overwhelmingly powerful? I might seem some old-world savage animal, only the more dreadful and disgusting for our common likeness–a foul creature to be incontinently slain.
`Already I saw other vast shapes–huge buildings with intricate parapets and tall columns, with a wooded hill-side dimly creeping in upon me through the lessening storm. I was seized with a panic fear. I turned frantically to the Time Machine, and strove hard to readjust it. As I did so the shafts of the sun smote through the thunderstorm. The grey downpour was swept aside and vanished like the trailing garments of a ghost. Above me, in the intense blue of the summer sky, some faint brown shreds of cloud whirled into nothingness. The great buildings about me stood out clear and distinct, shining with the wet of the thunderstorm, and picked out in white by the unmelted hailstones piled along their courses. I felt naked in a strange world. I felt as perhaps a bird may feel in the clear air, knowing the hawk wings above and will swoop. My fear grew to frenzy. I took a breathing space, set my teeth, and again grappled fiercely, wrist and knee, with the machine. It gave under my desperate onset and turned over. It struck my chin violently. One hand on the saddle, the other on the lever, I stood panting heavily in attitude to mount again.
`But with this recovery of a prompt retreat my courage recovered. I looked more curiously and less fearfully at this world of the remote future. In a circular opening, high up in the wall of the nearer house, I saw a group of figures clad in rich soft robes. They had seen me, and their faces were directed towards me.
`Then I heard voices approaching me. Coming through the bushes by the White Sphinx were the heads and shoulders of men running. One of these emerged in a pathway leading straight to the little lawn upon which I stood with my machine. He was a slight creature–perhaps four feet high–clad in a purple tunic, girdled at the waist with a leather belt. Sandals or buskins–I could not clearly distinguish which–were on his feet; his legs were bare to the knees, and his head was bare. Noticing that, I noticed for the first time how warm the air was.
`He struck me as being a very beautiful and graceful creature, but indescribably frail. His flushed face reminded me of the more beautiful kind of consumptive–that hectic beauty of which we used to hear so much. At the sight of him I suddenly regained confidence. I took my hands from the machine.
IV
`In another moment we were standing face to face, I and this fragile thing out of futurity. He came straight up to me and laughed into my eyes. The absence from his bearing of any sign of fear struck me at once. Then he turned to the two others who were following him and spoke to them in a strange and very sweet and liquid tongue.
`There were others coming, and presently a little group of perhaps eight or ten of these exquisite creatures were about me. One of them addressed me. It came into my head, oddly enough, that my voice was too harsh and deep for them. So I shook my head, and, pointing to my ears, shook it again. He came a step forward, hesitated, and then touched my hand. Then I felt other soft little tentacles upon my back and shoulders. They wanted to make sure I was real. There was nothing in this at all alarming. Indeed, there was something in these pretty little people that inspired confidence–a graceful gentleness, a certain childlike ease. And besides, they looked so frail that I could fancy myself flinging the whole dozen of them about like nine-pins. But I made a sudden motion to warn them when I saw their little pink hands feeling at the Time Machine. Happily then, when it was not too late, I thought of a danger I had hitherto forgotten, and reaching over the bars of the machine I unscrewed the little levers that would set it in motion, and put these in my pocket. Then I turned again to see what I could do in the way of communication.
`And then, looking more nearly into their features, I saw some further peculiarities in their Dresden-china type of prettiness. Their hair, which was uniformly curly, came to a sharp end at the neck and cheek; there was not the faintest suggestion of it on the face, and their ears were singularly minute. The mouths were small, with bright red, rather thin lips, and the little chins ran to a point. The eyes were large and mild; and–this may seem egotism on my part–I fancied even that there was a certain lack of the interest I might have expected in them.
`As they made no effort to communicate with me, but simply stood round me smiling and speaking in soft cooing notes to each other, I began the conversation. I pointed to the Time Machine and to myself. Then hesitating for a moment how to express time, I pointed to the sun. At once a quaintly pretty little figure in chequered purple and white followed my gesture, and then astonished me by imitating the sound of thunder.
`For a moment I was staggered, though the import of his gesture was plain enough. The question had come into my mind abruptly: were these creatures fools? You may hardly understand how it took me. You see I had always anticipated that the people of the year Eight Hundred and Two Thousand odd would be incredibly in front of us in knowledge, art, everything. Then one of them suddenly asked me a question that showed him to be on the intellectual level of one of our five-year-old children– asked me, in fact, if I had come from the sun in a thunderstorm! It let loose the judgment I had suspended upon their clothes, their frail light limbs, and fragile features. A flow of disappointment rushed across my mind. For a moment I felt that I had built the Time Machine in vain.
`I nodded, pointed to the sun, and gave them such a vivid rendering of a thunderclap as startled them. They all withdrew a pace or so and bowed. Then came one laughing towards me, carrying a chain of beautiful flowers altogether new to me, and put it about my neck. The idea was received with melodious applause; and presently they were all running to and fro for flowers, and laughingly flinging them upon me until I was almost smothered with blossom. You who have never seen the like can scarcely imagine what delicate and wonderful flowers countless years of culture had created. Then someone suggested that their plaything should be exhibited in the nearest building, and so I was led past the sphinx of white marble, which had seemed to watch me all the while with a smile at my astonishment, towards a vast grey edifice of fretted stone. As I went with them the memory of my confident anticipations of a profoundly grave and intellectual posterity came, with irresistible merriment, to my mind.
`The building had a huge entry, and was altogether of colossal dimensions. I was naturally most occupied with the growing crowd of little people, and with the big open portals that yawned before me shadowy and mysterious. My general impression of the world I saw over their heads was a tangled waste of beautiful bushes and flowers, a long neglected and yet weedless garden. I saw a number of tall spikes of strange white flowers, measuring a foot perhaps across the spread of the waxen petals. They grew scattered, as if wild, among the variegated shrubs, but, as I say, I did not examine them closely at this time. The Time Machine was left deserted on the turf among the rhododendrons.
`The arch of the doorway was richly carved, but naturally I did not observe the carving very narrowly, though I fancied I saw suggestions of old Phoenician decorations as I passed through, and it struck me that they were very badly broken and weather- worn. Several more brightly clad people met me in the doorway, and so we entered, I, dressed in dingy nineteenth-century garments, looking grotesque enough, garlanded with flowers, and surrounded by an eddying mass of bright, soft-colored robes and shining white limbs, in a melodious whirl of laughter and laughing speech.
`The big doorway opened into a proportionately great hall hung with brown. The roof was in shadow, and the windows, partially glazed with coloured glass and partially unglazed, admitted a tempered light. The floor was made up of huge blocks of some very hard white metal, not plates nor slabs–blocks, and it was so much worn, as I judged by the going to and fro of past generations, as to be deeply channelled along the more frequented ways. Transverse to the length were innumerable tables made of slabs of polished stone, raised perhaps a foot from the floor, and upon these were heaps of fruits. Some I recognized as a kind of hypertrophied raspberry and orange, but for the most part they were strange.
`Between the tables was scattered a great number of cushions. Upon these my conductors seated themselves, signing for me to do likewise. With a pretty absence of ceremony they began to eat the fruit with their hands, flinging peel and stalks, and so forth, into the round openings in the sides of the tables. I was not loath to follow their example, for I felt thirsty and hungry. As I did so I surveyed the hall at my leisure.
`And perhaps the thing that struck me most was its dilapidated look. The stained-glass windows, which displayed only a geometrical pattern, were broken in many places, and the curtains that hung across the lower end were thick with dust. And it caught my eye that the corner of the marble table near me was fractured. Nevertheless, the general effect was extremely rich and picturesque. There were, perhaps, a couple of hundred people dining in the hall, and most of them, seated as near to me as they could come, were watching me with interest, their little eyes shining over the fruit they were eating. All were clad in the same soft and yet strong, silky material.
`Fruit, by the by, was all their diet. These people of the remote future were strict vegetarians, and while I was with them, in spite of some carnal cravings, I had to be frugivorous also. Indeed, I found afterwards that horses, cattle, sheep, dogs, had followed the Ichthyosaurus into extinction. But the fruits were very delightful; one, in particular, that seemed to be in season all the time I was there–a floury thing in a three-sided husk –was especially good, and I made it my staple. At first I was puzzled by all these strange fruits, and by the strange flowers I saw, but later I began to perceive their import.
`However, I am telling you of my fruit dinner in the distant future now. So soon as my appetite was a little checked, I determined to make a resolute attempt to learn the speech of these new men of mine. Clearly that was the next thing to do. The fruits seemed a convenient thing to begin upon, and holding one of these up I began a series of interrogative sounds and gestures. I had some considerable difficulty in conveying my meaning. At first my efforts met with a stare of surprise or inextinguishable laughter, but presently a fair-haired little creature seemed to grasp my intention and repeated a name. They had to chatter and explain the business at great length to each other, and my first attempts to make the exquisite little sounds of their language caused an immense amount of amusement. However, I felt like a schoolmaster amidst children, and persisted, and presently I had a score of noun substantives at least at my command; and then I got to demonstrative pronouns, and even the verb “to eat.” But it was slow work, and the little people soon tired and wanted to get away from my interrogations, so I determined, rather of necessity, to let them give their lessons in little doses when they felt inclined. And very little doses I found they were before long, for I never met people more indolent or more easily fatigued.
`A queer thing I soon discovered about my little hosts, and that was their lack of interest. They would come to me with eager cries of astonishment, like children, but like children they would soon stop examining me and wander away after some other toy. The dinner and my conversational beginnings ended, I noted for the first time that almost all those who had surrounded me at first were gone. It is odd, too, how speedily I came to disregard these little people. I went out through the portal into the sunlit world again as soon as my hunger was satisfied. I was continually meeting more of these men of the future, who would follow me a little distance, chatter and laugh about me, and, having smiled and gesticulated in a friendly way, leave me again to my own devices.
`The calm of evening was upon the world as I emerged from the great hall, and the scene was lit by the warm glow of the setting sun. At first things were very confusing. Everything was so entirely different from the world I had known–even the flowers. The big building I had left was situated on the slope of a broad river valley, but the Thames had shifted perhaps a mile from its present position. I resolved to mount to the summit of a crest perhaps a mile and a half away, from which I could get a wider view of this our planet in the year Eight Hundred and Two Thousand Seven Hundred and One A.D. For that, I should explain, was the date the little dials of my machine recorded.
`As I walked I was watching for every impression that could possibly help to explain the condition of ruinous splendour in which I found the world–for ruinous it was. A little way up the hill, for instance, was a great heap of granite, bound together by masses of aluminium, a vast labyrinth of precipitous walls and crumpled heaps, amidst which were thick heaps of very beautiful pagoda-like plants–nettles possibly–but wonderfully tinted with brown about the leaves, and incapable of stinging. It was evidently the derelict remains of some vast structure, to what end built I could not determine. It was here that I was destined, at a later date, to have a very strange experience–the first intimation of a still stranger discovery–but of that I will speak in its proper place.
`Looking round with a sudden thought, from a terrace on which I rested for a while, I realized that there were no small houses to be seen. Apparently the single house, and possibly even the household, had vanished. Here and there among the greenery were palace-like buildings, but the house and the cottage, which form such characteristic features of our own English landscape, had disappeared.
`”Communism,” said I to myself.
`And on the heels of that came another thought. I looked at the half-dozen little figures that were following me. Then, in a flash, I perceived that all had the same form of costume, the same soft hairless visage, and the same girlish rotundity of limb. It may seem strange, perhaps, that I had not noticed this before. But everything was so strange. Now, I saw the fact plainly enough. In costume, and in all the differences of texture and bearing that now mark off the sexes from each other, these people of the future were alike. And the children seemed to my eyes to be but the miniatures of their parents. I judged, then, that the children of that time were extremely precocious, physically at least, and I found afterwards abundant verification of my opinion.
`Seeing the ease and security in which these people were living, I felt that this close resemblance of the sexes was after all what one would expect; for the strength of a man and the softness of a woman, the institution of the family, and the differentiation of occupations are mere militant necessities of an age of physical force; where population is balanced and abundant, much childbearing becomes an evil rather than a blessing to the State; where violence comes but rarely and off-spring are secure, there is less necessity–indeed there is no necessity–for an efficient family, and the specialization of the sexes with reference to their children’s needs disappears. We see some beginnings of this even in our own time, and in this future age it was complete. This, I must remind you, was my speculation at the time. Later, I was to appreciate how far it fell short of the reality.
`While I was musing upon these things, my attention was attracted by a pretty little structure, like a well under a cupola. I thought in a transitory way of the oddness of wells still existing, and then resumed the thread of my speculations. There were no large buildings towards the top of the hill, and as my walking powers were evidently miraculous, I was presently left alone for the first time. With a strange sense of freedom and adventure I pushed on up to the crest.
`There I found a seat of some yellow metal that I did not recognize, corroded in places with a kind of pinkish rust and half smothered in soft moss, the arm-rests cast and filed into the resemblance of griffins’ heads. I sat down on it, and I surveyed the broad view of our old world under the sunset of that long day. It was as sweet and fair a view as I have ever seen. The sun had already gone below the horizon and the west was flaming gold, touched with some horizontal bars of purple and crimson. Below was the valley of the Thames, in which the river lay like a band of burnished steel. I have already spoken of the great palaces dotted about among the variegated greenery, some in ruins and some still occupied. Here and there rose a white or silvery figure in the waste garden of the earth, here and there came the sharp vertical line of some cupola or obelisk. There were no hedges, no signs of proprietary rights, no evidences of agriculture; the whole earth had become a garden.
`So watching, I began to put my interpretation upon the things I had seen, and as it shaped itself to me that evening, my interpretation was something in this way. (Afterwards I found I had got only a half-truth–or only a glimpse of one facet of the truth.)
`It seemed to me that I had happened upon humanity upon the wane. The ruddy sunset set me thinking of the sunset of mankind. For the first time I began to realize an odd consequence of the social effort in which we are at present engaged. And yet, come to think, it is a logical consequence enough. Strength is the outcome of need; security sets a premium on feebleness. The work of ameliorating the conditions of life–the true civilizing process that makes life more and more secure–had gone steadily on to a climax. One triumph of a united humanity over Nature had followed another. Things that are now mere dreams had become projects deliberately put in hand and carried forward. And the harvest was what I saw!
`After all, the sanitation and the agriculture of to-day are still in the rudimentary stage. The science of our time has attacked but a little department of the field of human disease, but even so, it spreads its operations very steadily and persistently. Our agriculture and horticulture destroy a weed just here and there and cultivate perhaps a score or so of wholesome plants, leaving the greater number to fight out a balance as they can. We improve our favourite plants and animals –and how few they are–gradually by selective breeding; now a new and better peach, now a seedless grape, now a sweeter and larger flower, now a more convenient breed of cattle. We improve them gradually, because our ideals are vague and tentative, and our knowledge is very limited; because Nature, too, is shy and slow in our clumsy hands. Some day all this will be better organized, and still better. That is the drift of the current in spite of the eddies. The whole world will be intelligent, educated, and co-operating; things will move faster and faster towards the subjugation of Nature. In the end, wisely and carefully we shall readjust the balance of animal and vegetable to suit our human needs.
`This adjustment, I say, must have been done, and done well; done indeed for all Time, in the space of Time across which my machine had leaped. The air was free from gnats, the earth from weeds or fungi; everywhere were fruits and sweet and delightful flowers; brilliant butterflies flew hither and thither. The ideal of preventive medicine was attained. Diseases had been stamped out. I saw no evidence of any contagious diseases during all my stay. And I shall have to tell you later that even the processes of putrefaction and decay had been profoundly affected by these changes.
`Social triumphs, too, had been effected. I saw mankind housed in splendid shelters, gloriously clothed, and as yet I had found them engaged in no toil. There were no signs of struggle, neither social nor economical struggle. The shop, the advertisement, traffic, all that commerce which constitutes the body of our world, was gone. It was natural on that golden evening that I should jump at the idea of a social paradise. The difficulty of increasing population had been met, I guessed, and population had ceased to increase.
`But with this change in condition comes inevitably adaptations to the change. What, unless biological science is a mass of errors, is the cause of human intelligence and vigour? Hardship and freedom: conditions under which the active, strong, and subtle survive and the weaker go to the wall; conditions that put a premium upon the loyal alliance of capable men, upon self-restraint, patience, and decision. And the institution of the family, and the emotions that arise therein, the fierce jealousy, the tenderness for offspring, parental self-devotion, all found their justification and support in the imminent dangers of the young. NOW, where are these imminent dangers? There is a sentiment arising, and it will grow, against connubial jealousy, against fierce maternity, against passion of all sorts; unnecessary things now, and things that make us uncomfortable, savage survivals, discords in a refined and pleasant life.
`I thought of the physical slightness of the people, their lack of intelligence, and those big abundant ruins, and it strengthened my belief in a perfect conquest of Nature. For after the battle comes Quiet. Humanity had been strong, energetic, and intelligent, and had used all its abundant vitality to alter the conditions under which it lived. And now came the reaction of the altered conditions.
`Under the new conditions of perfect comfort and security, that restless energy, that with us is strength, would become weakness. Even in our own time certain tendencies and desires, once necessary to survival, are a constant source of failure. Physical courage and the love of battle, for instance, are no great help–may even be hindrances–to a civilized man. And in a state of physical balance and security, power, intellectual as well as physical, would be out of place. For countless years I judged there had been no danger of war or solitary violence, no danger from wild beasts, no wasting disease to require strength of constitution, no need of toil. For such a life, what we should call the weak are as well equipped as the strong, are indeed no longer weak. Better equipped indeed they are, for the strong would be fretted by an energy for which there was no outlet. No doubt the exquisite beauty of the buildings I saw was the outcome of the last surgings of the now purposeless energy of mankind before it settled down into perfect harmony with the conditions under which it lived–the flourish of that triumph which began the last great peace. This has ever been the fate of energy in security; it takes to art and to eroticism, and then come languor and decay.
`Even this artistic impetus would at last die away–had almost died in the Time I saw. To adorn themselves with flowers, to dance, to sing in the sunlight: so much was left of the artistic spirit, and no more. Even that would fade in the end into a contented inactivity. We are kept keen on the grindstone of pain and necessity, and, it seemed to me, that here was that hateful grindstone broken at last!
`As I stood there in the gathering dark I thought that in this simple explanation I had mastered the problem of the world– mastered the whole secret of these delicious people. Possibly the checks they had devised for the increase of population had succeeded too well, and their numbers had rather diminished than kept stationary. That would account for the abandoned ruins. Very simple was my explanation, and plausible enough–as most wrong theories are!
V
`As I stood there musing over this too perfect triumph of man, the full moon, yellow and gibbous, came up out of an overflow of silver light in the north-east. The bright little figures ceased to move about below, a noiseless owl flitted by, and I shivered with the chill of the night. I determined to descend and find where I could sleep.
`I looked for the building I knew. Then my eye travelled along to the figure of the White Sphinx upon the pedestal of bronze, growing distinct as the light of the rising moon grew brighter. I could see the silver birch against it. There was the tangle of rhododendron bushes, black in the pale light, and there was the little lawn. I looked at the lawn again. A queer doubt chilled my complacency. “No,” said I stoutly to myself, “that was not the lawn.”
`But it WAS the lawn. For the white leprous face of the sphinx was towards it. Can you imagine what I felt as this conviction came home to me? But you cannot. The Time Machine was gone!
`At once, like a lash across the face, came the possibility of losing my own age, of being left helpless in this strange new world. The bare thought of it was an actual physical sensation. I could feel it grip me at the throat and stop my breathing. In another moment I was in a passion of fear and running with great leaping strides down the slope. Once I fell headlong and cut my face; I lost no time in stanching the blood, but jumped up and ran on, with a warm trickle down my cheek and chin. All the time I ran I was saying to myself: “They have moved it a little, pushed it under the bushes out of the way.” Nevertheless, I ran with all my might. All the time, with the certainty that sometimes comes with excessive dread, I knew that such assurance was folly, knew instinctively that the machine was removed out of my reach. My breath came with pain. I suppose I covered the whole distance from the hill crest to the little lawn, two miles perhaps, in ten minutes. And I am not a young man. I cursed aloud, as I ran, at my confident folly in leaving the machine, wasting good breath thereby. I cried aloud, and none answered. Not a creature seemed to be stirring in that moonlit world.
`When I reached the lawn my worst fears were realized. Not a trace of the thing was to be seen. I felt faint and cold when I faced the empty space among the black tangle of bushes. I ran round it furiously, as if the thing might be hidden in a corner, and then stopped abruptly, with my hands clutching my hair. Above me towered the sphinx, upon the bronze pedestal, white, shining, leprous, in the light of the rising moon. It seemed to smile in mockery of my dismay.
`I might have consoled myself by imagining the little people had put the mechanism in some shelter for me, had I not felt assured of their physical and intellectual inadequacy. That is what dismayed me: the sense of some hitherto unsuspected power, through whose intervention my invention had vanished. Yet, for one thing I felt assured: unless some other age had produced its exact duplicate, the machine could not have moved in time. The attachment of the levers–I will show you the method later– prevented any one from tampering with it in that way when they were removed. It had moved, and was hid, only in space. But then, where could it be?
`I think I must have had a kind of frenzy. I remember running violently in and out among the moonlit bushes all round the sphinx, and startling some white animal that, in the dim light, I took for a small deer. I remember, too, late that night, beating the bushes with my clenched fist until my knuckles were gashed and bleeding from the broken twigs. Then, sobbing and raving in my anguish of mind, I went down to the great building of stone. The big hall was dark, silent, and deserted. I slipped on the uneven floor, and fell over one of the malachite tables, almost breaking my shin. I lit a match and went on past the dusty curtains, of which I have told you.
`There I found a second great hall covered with cushions, upon which, perhaps, a score or so of the little people were sleeping. I have no doubt they found my second appearance strange enough, coming suddenly out of the quiet darkness with inarticulate noises and the splutter and flare of a match. For they had forgotten about matches. “Where is my Time Machine?” I began, bawling like an angry child, laying hands upon them and shaking them up together. It must have been very queer to them. Some laughed, most of them looked sorely frightened. When I saw them standing round me, it came into my head that I was doing as foolish a thing as it was possible for me to do under the circumstances, in trying to revive the sensation of fear. For, reasoning from their daylight behaviour, I thought that fear must be forgotten.
`Abruptly, I dashed down the match, and, knocking one of the people over in my course, went blundering across the big dining-hall again, out under the moonlight. I heard cries of terror and their little feet running and stumbling this way and that. I do not remember all I did as the moon crept up the sky. I suppose it was the unexpected nature of my loss that maddened me. I felt hopelessly cut off from my own kind–a strange animal in an unknown world. I must have raved to and fro, screaming and crying upon God and Fate. I have a memory of horrible fatigue, as the long night of despair wore away; of looking in this impossible place and that; of groping among moon-lit ruins and touching strange creatures in the black shadows; at last, of lying on the ground near the sphinx and weeping with absolute wretchedness. I had nothing left but misery. Then I slept, and when I woke again it was full day, and a couple of sparrows were hopping round me on the turf within reach of my arm.
`I sat up in the freshness of the morning, trying to remember how I had got there, and why I had such a profound sense of desertion and despair. Then things came clear in my mind. With the plain, reasonable daylight, I could look my circumstances fairly in the face. I saw the wild folly of my frenzy overnight, and I could reason with myself. “Suppose the worst?” I said. “Suppose the machine altogether lost–perhaps destroyed? It behooves me to be calm and patient, to learn the way of the people, to get a clear idea of the method of my loss, and the means of getting materials and tools; so that in the end, perhaps, I may make another.” That would be my only hope, perhaps, but better than despair. And, after all, it was a beautiful and curious world.
`But probably, the machine had only been taken away. Still, I must be calm and patient, find its hiding-place, and recover it by force or cunning. And with that I scrambled to my feet and looked about me, wondering where I could bathe. I felt weary, stiff, and travel-soiled. The freshness of the morning made me desire an equal freshness. I had exhausted my emotion. Indeed, as I went about my business, I found myself wondering at my intense excitement overnight. I made a careful examination of the ground about the little lawn. I wasted some time in futile questionings, conveyed, as well as I was able, to such of the little people as came by. They all failed to understand my gestures; some were simply stolid, some thought it was a jest and laughed at me. I had the hardest task in the world to keep my hands off their pretty laughing faces. It was a foolish impulse, but the devil begotten of fear and blind anger was ill curbed and still eager to take advantage of my perplexity. The turf gave better counsel. I found a groove ripped in it, about midway between the pedestal of the sphinx and the marks of my feet where, on arrival, I had struggled with the overturned machine. There were other signs of removal about, with queer narrow footprints like those I could imagine made by a sloth. This directed my closer attention to the pedestal. It was, as I think I have said, of bronze. It was not a mere block, but highly decorated with deep framed panels on either side. I went and rapped at these. The pedestal was hollow. Examining the panels with care I found them discontinuous with the frames. There were no handles or keyholes, but possibly the panels, if they were doors, as I supposed, opened from within. One thing was clear enough to my mind. It took no very great mental effort to infer that my Time Machine was inside that pedestal. But how it got there was a different problem.
`I saw the heads of two orange-clad people coming through the bushes and under some blossom-covered apple-trees towards me. I turned smiling to them and beckoned them to me. They came, and then, pointing to the bronze pedestal, I tried to intimate my wish to open it. But at my first gesture towards this they behaved very oddly. I don’t know how to convey their expression to you. Suppose you were to use a grossly improper gesture to a delicate-minded woman–it is how she would look. They went off as if they had received the last possible insult. I tried a sweet-looking little chap in white next, with exactly the same result. Somehow, his manner made me feel ashamed of myself. But, as you know, I wanted the Time Machine, and I tried him once more. As he turned off, like the others, my temper got the better of me. In three strides I was after him, had him by the loose part of his robe round the neck, and began dragging him towards the sphinx. Then I saw the horror and repugnance of his face, and all of a sudden I let him go.
`But I was not beaten yet. I banged with my fist at the bronze panels. I thought I heard something stir inside–to be explicit, I thought I heard a sound like a chuckle–but I must have been mistaken. Then I got a big pebble from the river, and came and hammered till I had flattened a coil in the decorations, and the verdigris came off in powdery flakes. The delicate little people must have heard me hammering in gusty outbreaks a mile away on either hand, but nothing came of it. I saw a crowd of them upon the slopes, looking furtively at me. At last, hot and tired, I sat down to watch the place. But I was too restless to watch long; I am too Occidental for a long vigil. I could work at a problem for years, but to wait inactive for twenty-four hours–that is another matter.
`I got up after a time, and began walking aimlessly through the bushes towards the hill again. “Patience,” said I to myself. “If you want your machine again you must leave that sphinx alone. If they mean to take your machine away, it’s little good your wrecking their bronze panels, and if they don’t, you will get it back as soon as you can ask for it. To sit among all those unknown things before a puzzle like that is hopeless. That way lies monomania. Face this world. Learn its ways, watch it, be careful of too hasty guesses at its meaning. In the end you will find clues to it all.” Then suddenly the humour of the situation came into my mind: the thought of the years I had spent in study and toil to get into the future age, and now my passion of anxiety to get out of it. I had made myself the most complicated and the most hopeless trap that ever a man devised. Although it was at my own expense, I could not help myself. I laughed aloud.
`Going through the big palace, it seemed to me that the little people avoided me. It may have been my fancy, or it may have had something to do with my hammering at the gates of bronze. Yet I felt tolerably sure of the avoidance. I was careful, however, to show no concern and to abstain from any pursuit of them, and in the course of a day or two things got back to the old footing. I made what progress I could in the language, and in addition I pushed my explorations here and there. Either I missed some subtle point or their language was excessively simple–almost exclusively composed of concrete substantives and verbs. There seemed to be few, if any, abstract terms, or little use of figurative language. Their sentences were usually simple and of two words, and I failed to convey or understand any but the simplest propositions. I determined to put the thought of my Time Machine and the mystery of the bronze doors under the sphinx as much as possible in a corner of memory, until my growing knowledge would lead me back to them in a natural way. Yet a certain feeling, you may understand, tethered me in a circle of a few miles round the point of my arrival.
`So far as I could see, all the world displayed the same exuberant richness as the Thames valley. From every hill I climbed I saw the same abundance of splendid buildings, endlessly varied in material and style, the same clustering thickets of evergreens, the same blossom-laden trees and tree-ferns. Here and there water shone like silver, and beyond, the land rose into blue undulating hills, and so faded into the serenity of the sky. A peculiar feature, which presently attracted my attention, was the presence of certain circular wells, several, as it seemed to me, of a very great depth. One lay by the path up the hill, which I had followed during my first walk. Like the others, it was rimmed with bronze, curiously wrought, and protected by a little cupola from the rain. Sitting by the side of these wells, and peering down into the shafted darkness, I could see no gleam of water, nor could I start any reflection with a lighted match. But in all of them I heard a certain sound: a thud-thud-thud, like the beating of some big engine; and I discovered, from the flaring of my matches, that a steady current of air set down the shafts. Further, I threw a scrap of paper into the throat of one, and, instead of fluttering slowly down, it was at once sucked swiftly out of sight.
`After a time, too, I came to connect these wells with tall towers standing here and there upon the slopes; for above them there was often just such a flicker in the air as one sees on a hot day above a sun-scorched beach. Putting things together, I reached a strong suggestion of an extensive system of subterranean ventilation, whose true import it was difficult to imagine. I was at first inclined to associate it with the sanitary apparatus of these people. It was an obvious conclusion, but it was absolutely wrong.
`And here I must admit that I learned very little of drains and bells and modes of conveyance, and the like conveniences, during my time in this real future. In some of these visions of Utopias and coming times which I have read, there is a vast amount of detail about building, and social arrangements, and so forth. But while such details are easy enough to obtain when the whole world is contained in one’s imagination, they are altogether inaccessible to a real traveller amid such realities as I found here. Conceive the tale of London which a negro, fresh from Central Africa, would take back to his tribe! What would he know of railway companies, of social movements, of telephone and telegraph wires, of the Parcels Delivery Company, and postal orders and the like? Yet we, at least, should be willing enough to explain these things to him! And even of what he knew, how much could he make his untravelled friend either apprehend or believe? Then, think how narrow the gap between a negro and a white man of our own times, and how wide the interval between myself and these of the Golden Age! I was sensible of much which was unseen, and which contributed to my comfort; but save for a general impression of automatic organization, I fear I can convey very little of the difference to your mind.
`In the matter of sepulchre, for instance, I could see no signs of crematoria nor anything suggestive of tombs. But it occurred to me that, possibly, there might be cemeteries (or crematoria) somewhere beyond the range of my explorings. This, again, was a question I deliberately put to myself, and my curiosity was at first entirely defeated upon the point. The thing puzzled me, and I was led to make a further remark, which puzzled me still more: that aged and infirm among this people there were none.
`I must confess that my satisfaction with my first theories of an automatic civilization and a decadent humanity did not long endure. Yet I could think of no other. Let me put my difficulties. The several big palaces I had explored were mere living places, great dining-halls and sleeping apartments. I could find no machinery, no appliances of any kind. Yet these people were clothed in pleasant fabrics that must at times need renewal, and their sandals, though undecorated, were fairly complex specimens of metalwork. Somehow such things must be made. And the little people displayed no vestige of a creative tendency. There were no shops, no workshops, no sign of importations among them. They spent all their time in playing gently, in bathing in the river, in making love in a half-playful fashion, in eating fruit and sleeping. I could not see how things were kept going.
`Then, again, about the Time Machine: something, I knew not what, had taken it into the hollow pedestal of the White Sphinx. Why? For the life of me I could not imagine. Those waterless wells, too, those flickering pillars. I felt I lacked a clue. I felt–how shall I put it? Suppose you found an inscription, with sentences here and there in excellent plain English, and interpolated therewith, others made up of words, of letters even, absolutely unknown to you? Well, on the third day of my visit, that was how the world of Eight Hundred and Two Thousand Seven Hundred and One presented itself to me!
`That day, too, I made a friend–of a sort. It happened that, as I was watching some of the little people bathing in a shallow, one of them was seized with cramp and began drifting downstream. The main current ran rather swiftly, but not too strongly for even a moderate swimmer. It will give you an idea, therefore, of the strange deficiency in these creatures, when I tell you that none made the slightest attempt to rescue the weakly crying little thing which was drowning before their eyes. When I realized this, I hurriedly slipped off my clothes, and, wading in at a point lower down, I caught the poor mite and drew her safe to land. A little rubbing of the limbs soon brought her round, and I had the satisfaction of seeing she was all right before I left her. I had got to such a low estimate of her kind that I did not expect any gratitude from her. In that, however, I was wrong.
`This happened in the morning. In the afternoon I met my little woman, as I believe it was, as I was returning towards my centre from an exploration, and she received me with cries of delight and presented me with a big garland of flowers– evidently made for me and me alone. The thing took my imagination. Very possibly I had been feeling desolate. At any rate I did my best to display my appreciation of the gift. We were soon seated together in a little stone arbour, engaged in conversation, chiefly of smiles. The creature’s friendliness affected me exactly as a child’s might have done. We passed each other flowers, and she kissed my hands. I did the same to hers. Then I tried talk, and found that her name was Weena, which, though I don’t know what it meant, somehow seemed appropriate enough. That was the beginning of a queer friendship which lasted a week, and ended–as I will tell you!
`She was exactly like a child. She wanted to be with me always. She tried to follow me everywhere, and on my next journey out and about it went to my heart to tire her down, and leave her at last, exhausted and calling after me rather plaintively. But the problems of the world had to be mastered. I had not, I said to myself, come into the future to carry on a miniature flirtation. Yet her distress when I left her was very great, her expostulations at the parting were sometimes frantic, and I think, altogether, I had as much trouble as comfort from her devotion. Nevertheless she was, somehow, a very great comfort. I thought it was mere childish affection that made her cling to me. Until it was too late, I did not clearly know what I had inflicted upon her when I left her. Nor until it was too late did I clearly understand what she was to me. For, by merely seeming fond of me, and showing in her weak, futile way that she cared for me, the little doll of a creature presently gave my return to the neighbourhood of the White Sphinx almost the feeling of coming home; and I would watch for her tiny figure of white and gold so soon as I came over the hill.
`It was from her, too, that I learned that fear had not yet left the world. She was fearless enough in the daylight, and she had the oddest confidence in me; for once, in a foolish moment, I made threatening grimaces at her, and she simply laughed at them. But she dreaded the dark, dreaded shadows, dreaded black things. Darkness to her was the one thing dreadful. It was a singularly passionate emotion, and it set me thinking and observing. I discovered then, among other things, that these little people gathered into the great houses after dark, and slept in droves. To enter upon them without a light was to put them into a tumult of apprehension. I never found one out of doors, or one sleeping alone within doors, after dark. Yet I was still such a blockhead that I missed the lesson of that fear, and in spite of Weena’s distress I insisted upon sleeping away from these slumbering multitudes.
`It troubled her greatly, but in the end her odd affection for me triumphed, and for five of the nights of our acquaintance, including the last night of all, she slept with her head pillowed on my arm. But my story slips away from me as I speak of her. It must have been the night before her rescue that I was awakened about dawn. I had been restless, dreaming most disagreeably that I was drowned, and that sea anemones were feeling over my face with their soft palps. I woke with a start, and with an odd fancy that some greyish animal had just rushed out of the chamber. I tried to get to sleep again, but I felt restless and uncomfortable. It was that dim grey hour when things are just creeping out of darkness, when everything is colourless and clear cut, and yet unreal. I got up, and went down into the great hall, and so out upon the flagstones in front of the palace. I thought I would make a virtue of necessity, and see the sunrise.
`The moon was setting, and the dying moonlight and the first pallor of dawn were mingled in a ghastly half-light. The bushes were inky black, the ground a sombre grey, the sky colourless and cheerless. And up the hill I thought I could see ghosts. There several times, as I scanned the slope, I saw white figures. Twice I fancied I saw a solitary white, ape-like creature running rather quickly up the hill, and once near the ruins I saw a leash of them carrying some dark body. They moved hastily. I did not see what became of them. It seemed that they vanished among the bushes. The dawn was still indistinct, you must understand. I was feeling that chill, uncertain, early-morning feeling you may have known. I doubted my eyes.
`As the eastern sky grew brighter, and the light of the day came on and its vivid colouring returned upon the world once more, I scanned the view keenly. But I saw no vestige of my white figures. They were mere creatures of the half light. “They must have been ghosts,” I said; “I wonder whence they dated.” For a queer notion of Grant Allen’s came into my head, and amused me. If each generation die and leave ghosts, he argued, the world at last will get overcrowded with them. On that theory they would have grown innumerable some Eight Hundred Thousand Years hence, and it was no great wonder to see four at once. But the jest was unsatisfying, and I was thinking of these figures all the morning, until Weena’s rescue drove them out of my head. I associated them in some indefinite way with the white animal I had startled in my first passionate search for the Time Machine. But Weena was a pleasant substitute. Yet all the same, they were soon destined to take far deadlier possession of my mind.
`I think I have said how much hotter than our own was the weather of this Golden Age. I cannot account for it. It may be that the sun was hotter, or the earth nearer the sun. It is usual to assume that the sun will go on cooling steadily in the future. But people, unfamiliar with such speculations as those of the younger Darwin, forget that the planets must ultimately fall back one by one into the parent body. As these catastrophes occur, the sun will blaze with renewed energy; and it may be that some inner planet had suffered this fate. Whatever the reason, the fact remains that the sun was very much hotter than we know it.
`Well, one very hot morning–my fourth, I think–as I was seeking shelter from the heat and glare in a colossal ruin near the great house where I slept and fed, there happened this strange thing: Clambering among these heaps of masonry, I found a narrow gallery, whose end and side windows were blocked by fallen masses of stone. By contrast with the brilliancy outside, it seemed at first impenetrably dark to me. I entered it groping, for the change from light to blackness made spots of colour swim before me. Suddenly I halted spellbound. A pair of eyes, luminous by reflection against the daylight without, was watching me out of the darkness.
`The old instinctive dread of wild beasts came upon me. I clenched my hands and steadfastly looked into the glaring eyeballs. I was afraid to turn. Then the thought of the absolute security in which humanity appeared to be living came to my mind. And then I remembered that strange terror of the dark. Overcoming my fear to some extent, I advanced a step and spoke. I will admit that my voice was harsh and ill-controlled. I put out my hand and touched something soft. At once the eyes darted sideways, and something white ran past me. I turned with my heart in my mouth, and saw a queer little ape-like figure, its head held down in a peculiar manner, running across the sunlit space behind me. It blundered against a block of granite, staggered aside, and in a moment was hidden in a black shadow beneath another pile of ruined masonry.
`My impression of it is, of course, imperfect; but I know it was a dull white, and had strange large greyish-red eyes; also that there was flaxen hair on its head and down its back. But, as I say, it went too fast for me to see distinctly. I cannot even say whether it ran on all-fours, or only with its forearms held very low. After an instant’s pause I followed it into the second heap of ruins. I could not find it at first; but, after a time in the profound obscurity, I came upon one of those round well-like openings of which I have told you, half closed by a fallen pillar. A sudden thought came to me. Could this Thing have vanished down the shaft? I lit a match, and, looking down, I saw a small, white, moving creature, with large bright eyes which regarded me steadfastly as it retreated. It made me shudder. It was so like a human spider! It was clambering down the wall, and now I saw for the first time a number of metal foot and hand rests forming a kind of ladder down the shaft. Then the light burned my fingers and fell out of my hand, going out as it dropped, and when I had lit another the little monster had disappeared.
`I do not know how long I sat peering down that well. It was not for some time that I could succeed in persuading myself that the thing I had seen was human. But, gradually, the truth dawned on me: that Man had not remained one species, but had differentiated into two distinct animals: that my graceful children of the Upper-world were not the sole descendants of our generation, but that this bleached, obscene, nocturnal Thing, which had flashed before me, was also heir to all the ages.
`I thought of the flickering pillars and of my theory of an underground ventilation. I began to suspect their true import. And what, I wondered, was this Lemur doing in my scheme of a perfectly balanced organization? How was it related to the indolent serenity of the beautiful Upper-worlders? And what was hidden down there, at the foot of that shaft? I sat upon the edge of the well telling myself that, at any rate, there was nothing to fear, and that there I must descend for the solution of my difficulties. And withal I was absolutely afraid to go! As I hesitated, two of the beautiful Upper-world people came running in their amorous sport across the daylight in the shadow. The male pursued the female, flinging flowers at her as he ran.
`They seemed distressed to find me, my arm against the overturned pillar, peering down the well. Apparently it was considered bad form to remark these apertures; for when I pointed to this one, and tried to frame a question about it in their tongue, they were still more visibly distressed and turned away. But they were interested by my matches, and I struck some to amuse them. I tried them again about the well, and again I failed. So presently I left them, meaning to go back to Weena, and see what I could get from her. But my mind was already in revolution; my guesses and impressions were slipping and sliding to a new adjustment. I had now a clue to the import of these wells, to the ventilating towers, to the mystery of the ghosts; to say nothing of a hint at the meaning of the bronze gates and the fate of the Time Machine! And very vaguely there came a suggestion towards the solution of the economic problem that had puzzled me.
`Here was the new view. Plainly, this second species of Man was subterranean. There were three circumstances in particular which made me think that its rare emergence above ground was the outcome of a long-continued underground habit. In the first place, there was the bleached look common in most animals that live largely in the dark–the white fish of the Kentucky caves, for instance. Then, those large eyes, with that capacity for reflecting light, are common features of nocturnal things– witness the owl and the cat. And last of all, that evident confusion in the sunshine, that hasty yet fumbling awkward flight towards dark shadow, and that peculiar carriage of the head while in the light–all reinforced the theory of an extreme sensitiveness of the retina.
`Beneath my feet, then, the earth must be tunnelled enormously, and these tunnellings were the habitat of the new race. The presence of ventilating shafts and wells along the hill slopes–everywhere, in fact except along the river valley –showed how universal were its ramifications. What so natural, then, as to assume that it was in this artificial Underworld that such work as was necessary to the comfort of the daylight race was done? The notion was so plausible that I at once accepted it, and went on to assume the how of this splitting of the human species. I dare say you will anticipate the shape of my theory; though, for myself, I very soon felt that it fell far short of the truth.
`At first, proceeding from the problems of our own age, it seemed clear as daylight to me that the gradual widening of the present merely temporary and social difference between the Capitalist and the Labourer, was the key to the whole position. No doubt it will seem grotesque enough to you–and wildly incredible!–and yet even now there are existing circumstances to point that way. There is a tendency to utilize underground space for the less ornamental purposes of civilization; there is the Metropolitan Railway in London, for instance, there are new electric railways, there are subways, there are underground workrooms and restaurants, and they increase and multiply. Evidently, I thought, this tendency had increased till Industry had gradually lost its birthright in the sky. I mean that it had gone deeper and deeper into larger and ever larger underground factories, spending a still-increasing amount of its time therein, till, in the end–! Even now, does not an East-end worker live in such artificial conditions as practically to be cut off from the natural surface of the earth?
`Again, the exclusive tendency of richer people–due, no doubt, to the increasing refinement of their education, and the widening gulf between them and the rude violence of the poor– is already leading to the closing, in their interest, of considerable portions of the surface of the land. About London, for instance, perhaps half the prettier country is shut in against intrusion. And this same widening gulf–which is due to the length and expense of the higher educational process and the increased facilities for and temptations towards refined habits on the part of the rich–will make that exchange between class and class, that promotion by intermarriage which at present retards the splitting of our species along lines of social stratification, less and less frequent. So, in the end, above ground you must have the Haves, pursuing pleasure and comfort and beauty, and below ground the Have-nots, the Workers getting continually adapted to the conditions of their labour. Once they were there, they would no doubt have to pay rent, and not a little of it, for the ventilation of their caverns; and if they refused, they would starve or be suffocated for arrears. Such of them as were so constituted as to be miserable and rebellious would die; and, in the end, the balance being permanent, the survivors would become as well adapted to the conditions of underground life, and as happy in their way, as the Upper-world people were to theirs. As it seemed to me, the refined beauty and the etiolated pallor followed naturally enough.
`The great triumph of Humanity I had dreamed of took a different shape in my mind. It had been no such triumph of moral education and general co-operation as I had imagined. Instead, I saw a real aristocracy, armed with a perfected science and working to a logical conclusion the industrial system of to-day. Its triumph had not been simply a triumph over Nature, but a triumph over Nature and the fellow-man. This, I must warn you, was my theory at the time. I had no convenient cicerone in the pattern of the Utopian books. My explanation may be absolutely wrong. I still think it is the most plausible one. But even on this supposition the balanced civilization that was at last attained must have long since passed its zenith, and was now far fallen into decay. The too-perfect security of the Upper-worlders had led them to a slow movement of degeneration, to a general dwindling in size, strength, and intelligence. That I could see clearly enough already. What had happened to the Under-grounders I did not yet suspect; but from what I had seen of the Morlocks–that, by the by, was the name by which these creatures were called–I could imagine that the modification of the human type was even far more profound than among the “Eloi,” the beautiful race that I already knew.
`Then came troublesome doubts. Why had the Morlocks taken my Time Machine? For I felt sure it was they who had taken it. Why, too, if the Eloi were masters, could they not restore the machine to me? And why were they so terribly afraid of the dark? I proceeded, as I have said, to question Weena about this Under-world, but here again I was disappointed. At first she would not understand my questions, and presently she refused to answer them. She shivered as though the topic was unendurable. And when I pressed her, perhaps a little harshly, she burst into tears. They were the only tears, except my own, I ever saw in that Golden Age. When I saw them I ceased abruptly to trouble about the Morlocks, and was only concerned in banishing these signs of the human inheritance from Weena’s eyes. And very soon she was smiling and clapping her hands, while I solemnly burned a match.
VI
`It may seem odd to you, but it was two days before I could follow up the new-found clue in what was manifestly the proper way. I felt a peculiar shrinking from those pallid bodies. They were just the half-bleached colour of the worms and things one sees preserved in spirit in a zoological museum. And they were filthily cold to the touch. Probably my shrinking was largely due to the sympathetic influence of the Eloi, whose disgust of the Morlocks I now began to appreciate.
`The next night I did not sleep well. Probably my health was a little disordered. I was oppressed with perplexity and doubt. Once or twice I had a feeling of intense fear for which I could perceive no definite reason. I remember creeping noiselessly into the great hall where the little people were sleeping in the moonlight–that night Weena was among them–and feeling reassured by their presence. It occurred to me even then, that in the course of a few days the moon must pass through its last quarter, and the nights grow dark, when the appearances of these unpleasant creatures from below, these whitened Lemurs, this new vermin that had replaced the old, might be more abundant. And on both these days I had the restless feeling of one who shirks an inevitable duty. I felt assured that the Time Machine was only to be recovered by boldly penetrating these underground mysteries. Yet I could not face the mystery. If only I had had a companion it would have been different. But I was so horribly alone, and even to clamber down into the darkness of the well appalled me. I don’t know if you will understand my feeling, but I never felt quite safe at my back.
`It was this restlessness, this insecurity, perhaps, that drove me further and further afield in my exploring expeditions. Going to the south-westward towards the rising country that is now called Combe Wood, I observed far off, in the direction of nineteenth-century Banstead, a vast green structure, different in character from any I had hitherto seen. It was larger than the largest of the palaces or ruins I knew, and the facade had an Oriental look: the face of it having the lustre, as well as the pale-green tint, a kind of bluish-green, of a certain type of Chinese porcelain. This difference in aspect suggested a difference in use, and I was minded to push on and explore. But the day was growing late, and I had come upon the sight of the place after a long and tiring circuit; so I resolved to hold over the adventure for the following day, and I returned to the welcome and the caresses of little Weena. But next morning I perceived clearly enough that my curiosity regarding the Palace of Green Porcelain was a piece of self-deception, to enable me to shirk, by another day, an experience I dreaded. I resolved I would make the descent without further waste of time, and started out in the early morning towards a well near the ruins of granite and aluminium.
`Little Weena ran with me. She danced beside me to the well, but when she saw me lean over the mouth and look downward, she seemed strangely disconcerted. “Good-bye, Little Weena,” I said, kissing her; and then putting her down, I began to feel over the parapet for the climbing hooks. Rather hastily, I may as well confess, for I feared my courage might leak away! At first she watched me in amazement. Then she gave a most piteous cry, and running to me, she began to pull at me with her little hands. I think her opposition nerved me rather to proceed. I shook her off, perhaps a little roughly, and in another moment I was in the throat of the well. I saw her agonized face over the parapet, and smiled to reassure her. Then I had to look down at the unstable hooks to which I clung.
`I had to clamber down a shaft of perhaps two hundred yards. The descent was effected by means of metallic bars projecting from the sides of the well, and these being adapted to the needs of a creature much smaller and lighter than myself, I was speedily cramped and fatigued by the descent. And not simply fatigued! One of the bars bent suddenly under my weight, and almost swung me off into the blackness beneath. For a moment I hung by one hand, and after that experience I did not dare to rest again. Though my arms and back were presently acutely painful, I went on clambering down the sheer descent with as quick a motion as possible. Glancing upward, I saw the aperture, a small blue disk, in which a star was visible, while little Weena’s head showed as a round black projection. The thudding sound of a machine below grew louder and more oppressive. Everything save that little disk above was profoundly dark, and when I looked up again Weena had disappeared.
`I was in an agony of discomfort. I had some thought of trying to go up the shaft again, and leave the Under-world alone. But even while I turned this over in my mind I continued to descend. At last, with intense relief, I saw dimly coming up, a foot to the right of me, a slender loophole in the wall. Swinging myself in, I found it was the aperture of a narrow horizontal tunnel in which I could lie down and rest. It was not too soon. My arms ached, my back was cramped, and I was trembling with the prolonged terror of a fall. Besides this, the unbroken darkness had had a distressing effect upon my eyes. The air was full of the throb and hum of machinery pumping air down the shaft.
`I do not know how long I lay. I was roused by a soft hand touching my face. Starting up in the darkness I snatched at my matches and, hastily striking one, I saw three stooping white creatures similar to the one I had seen above ground in the ruin, hastily retreating before the light. Living, as they did, in what appeared to me impenetrable darkness, their eyes were abnormally large and sensitive, just as are the pupils of the abysmal fishes, and they reflected the light in the same way. I have no doubt they could see me in that rayless obscurity, and they did not seem to have any fear of me apart from the light. But, so soon as I struck a match in order to see them, they fled incontinently, vanishing into dark gutters and tunnels, from which their eyes glared at me in the strangest fashion.
`I tried to call to them, but the language they had was apparently different from that of the Over-world people; so that I was needs left to my own unaided efforts, and the thought of flight before exploration was even then in my mind. But I said to myself, “You are in for it now,” and, feeling my way along the tunnel, I found the noise of machinery grow louder. Presently the walls fell away from me, and I came to a large open space, and striking another match, saw that I had entered a vast arched cavern, which stretched into utter darkness beyond the range of my light. The view I had of it was as much as one could see in the burning of a match.
`Necessarily my memory is vague. Great shapes like big
-
 @ d34e832d:383f78d0
2025-03-07 00:01:02
@ d34e832d:383f78d0
2025-03-07 00:01:02[npub16d8gxt2z4k9e8sdpc0yyqzf5gp0np09ls4lnn630qzxzvwpl0rgq5h4rzv]
Helical Visualization of Time's Passage in Orbital Motion and Celestial Mechanics
Exploring the dynamics of our Solar System through helical visualization opens new possibilities for understanding time, orbital motion, and planetary trajectories. By visualizing time as a continuous helical path, we gain insights into the cyclical and evolving nature of celestial mechanics, where each planet's orbit interacts with others in both predictable and dynamic patterns.
1. Helical Visualization of Time’s Passage
- Time as a Continuous Helix: Instead of viewing planetary orbits as fixed ellipses, this model represents the passage of time as a helical curve, linking each orbital cycle to the next. This visualization allows for a deeper understanding of the long-term movement of celestial bodies.
- Progression of Orbital Events: As planets follow their helical paths, we can track the passage of time from multiple perspectives, observing how their positions and velocities evolve in relation to one another. The helical model offers an elegant representation of periodic cycles that emphasizes the interconnectedness of cosmic events.
- Temporal Interactions: In this model, events like eclipses, conjunctions, and retrogrades become visualized as intersecting points on the helical path, emphasizing their importance in the grand tapestry of the Solar System's motion.
2. Orbital Motion and Celestial Mechanics
- Interplanetary Influences: The interactions between planetary bodies are inherently governed by gravitational forces, which create orbital motions that are often predictable yet influenced by external factors like planetary alignments and the gravitational pull of distant stars.
- Orbital Resonance and Tidal Forces: The gravitational interactions between planets, moons, and even asteroids can result in phenomena like orbital resonance. These interactions can be visualized in a helical model, showing how bodies can affect each other's orbits over time, much like the push and pull of a dance.
- The Dance of the Planets: Each planet’s orbit is not only a path through space but a part of a cosmic ballet, where their gravitational interactions affect one another's orbits. The helical model of motion helps us visualize how these interactions evolve over millions of years, helping to predict future trajectories.
3. Planetary Orbits and the Structure of the Solar System
- Elliptical and Spiral Patterns: While many planetary orbits are elliptical, the helical model introduces a dynamic spiral element to represent the combined motion of planets both around the Sun and through space. As the planets move, their orbits could resemble intricate spirals that reflect the cumulative effect of their motion through time.
- Resonance and Stability: Certain orbits may stabilize or shift over long periods due to gravitational interactions between planets. This helical view provides a tool for observing how minor orbital shifts can amplify over time, affecting not only the planets but the overall structure of the Solar System.
- Nonlinear Progression: Planets do not follow predictable paths in a simple two-dimensional plane. Instead, their orbits are affected by multiple forces, including interactions with other celestial bodies, making the helical model an ideal tool for visualizing the complexity and evolving nature of these planetary orbits.
4. Space Visualization and the Expanding Universe
- Moving Beyond the Solar System: The helical model of time and orbital motion does not end with our Solar System. As we visualize the movement of our Solar System within the broader context of the Milky Way, we begin to understand how our own galaxy's orbit affects our local motion through the universe.
- Helical Paths in Cosmic Space: This visualization method allows us to consider the Solar System’s motion as part of a larger, spiraling pattern that reaches across the galaxy, suggesting that our journey through space follows an intricate, three-dimensional helical path.
Connections (Links to Other Notes)
- The Mathematical Foundations of Orbital Mechanics
- Time as a Dimension in Celestial Navigation
- Gravitational Forces and Orbital Stability
Tags
SolarSystem #HelicalMotion #TimeVisualization #OrbitalMechanics #CelestialBodies #PlanetaryOrbits #SpaceExploration
Donations via
- ZeroSumFreeParity@primal.net
-
 @ b8a9df82:6ab5cbbd
2025-03-06 22:39:15
@ b8a9df82:6ab5cbbd
2025-03-06 22:39:15Last week at Bitcoin Investment Week in New York City, hosted by Anthony Pompliano, Jack Mallers walked in wearing sneakers and a T-shirt, casually dropping, “Man… I hate politics.”
That was it. That was the moment I felt aligned again. That’s the energy I came for. No suits. No corporate jargon. Just a guy who gets it—who cares about people, bringing Bitcoin-powered payments to the masses and making sure people can actually use it.
His presence was a reminder of why we’re here in the first place. And his words—“I hate politics”—were a breath of fresh air.
Now, don’t get me wrong. Anthony was a fantastic host. His ability to mix wittiness, playfulness, and seriousness made him an entertaining moderator. But this week was unlike anything I’ve ever experienced in the Bitcoin ecosystem.
One of the biggest letdowns was the lack of interaction. No real Q&A sessions, no direct engagement, no real discussions. Just one fireside chat after another.
And sure, I get it—people love to hear themselves talk. But where were the questions? The critical debates? The chance for the audience to actually participate?
I’m used to Bitcoin meetups and conferences where you walk away with new ideas, new friends, and maybe even a new project to contribute to. Here, it was more like sitting in an expensive lecture hall, watching a lineup of speakers tell us things we already know.
A different vibe—and not in a good way
Over the past few months, I’ve attended nearly ten Bitcoin conferences, each leaving me feeling uplifted, inspired, and ready to take action. But this? This felt different. And not in a good way.
If this had been my first Bitcoin event, I might have walked away questioning whether I even belonged here. It wasn’t Prague. It wasn’t Riga. It wasn’t the buzzing, grassroots, pleb-filled gatherings I had grown to love. Instead, it felt more like a Wall Street networking event disguised as a Bitcoin conference.
Maybe it was the suits.
Or the fact that I was sitting in a room full of investors who have no problem dropping $1,000+ on a ticket.
Or that it reminded me way too much of my former life—working as a manager in London’s real estate industry, navigating boardrooms full of finance guys in polished shoes, talking about “assets under management.”
Bitcoin isn’t just an investment thesis. It’s a revolution. A movement. And yet, at times during this week, I felt like I was back in my fiat past, stuck in a room where people measured success in dollars, not in freedom.
Maybe that’s the point. Bitcoin Investment Week was never meant to be a pleb gathering.
That said, the week did have some bright spots. PubKey was a fantastic kickoff. That was real Bitcoin culture—plebs, Nostr, grassroots energy. People who actually use Bitcoin, not just talk about it.
But the absolute highlight? Jack Mallers, sneakers and all, cutting through the noise with his authenticity.
So, why did we even go?
Good question. Maybe it was curiosity. Maybe it was stepping out of our usual circles to see Bitcoin through a different lens. Maybe it was to remind ourselves why we chose this path in the first place.
Would I go again? Probably not.
Would I trade Prague, Riga, bitcoin++ or any of the grassroots Bitcoin conferences for this? Not a chance.
At the end of the day, Bitcoin doesn’t belong to Wall Street from my opinion. It belongs to the people who actually use it. And those are the people I want to be around.
-
 @ 000002de:c05780a7
2025-03-06 22:15:39
@ 000002de:c05780a7
2025-03-06 22:15:39Been hearing clips of Newsom's new podcast. I've long said Newsom will run for president. I was saying this when he was the mayor of San Fransisco. He is like a modern day Bill Clinton. He is VERY gifted with the skills a politician needs. He's cool and calm. He's quick and sharp. His podcast isn't terrible and he's talking to people that disagree with him. He is also pissing off the more extreme members of his party by his pivots on many issues. He's even talking about men in women's sports.
Make no mistake. I think the dude is a snake and criminal. I hope he never gets any other political office. I just think MANY, most people on the right underestimate this man. Had the Biden crime family actually cared about their party they would have stepped down and let Newsom run. I think he would have defeated Trump.
I know that will piss many of you off but I do not believe the US changed because the Orange man won an election. Trump was shooting fish in a barrel in the last election. Two attempts were made on his life. Biden ran the US into the ground. Harris is a joke. Newsom is not. Newsom is not a radical. He will move to the center and that will appeal to lot of people. Fools, but they are what they are.
originally posted at https://stacker.news/items/906052
-
 @ d34e832d:383f78d0
2025-03-06 21:57:23
@ d34e832d:383f78d0
2025-03-06 21:57:23https://pub-53ed77d5544b46628691823c1795f2c7.r2.dev/Reticulum-Unstoppable-Network-Compressed.mp4
[npub16d8gxt2z4k9e8sdpc0yyqzf5gp0np09ls4lnn630qzxzvwpl0rgq5h4rzv]
What is Reticulum?
Reticulum is a cryptographic networking stack designed for resilient, decentralized, and censorship-resistant communication. Unlike the traditional internet, Reticulum enables fully independent digital communications over various physical mediums, such as radio, LoRa, serial links, and even TCP/IP.
The key advantages of Reticulum include:
- Decentralization – No reliance on centralized infrastructure.
- Encryption & Privacy – End-to-end encryption built-in.
- Resilience – Operates over unreliable and low-bandwidth links.
- Interoperability – Works over WiFi, LoRa, Bluetooth, and more.
- Ease of Use – Can run on minimal hardware, including Raspberry Pi and embedded devices.Reticulum is ideal for off-grid, censorship-resistant communications, emergency preparedness, and secure messaging.
1. Getting Started with Reticulum
To quickly get started with Reticulum, follow the official guide:
Reticulum: Getting Started FastStep 1: Install Reticulum
On Linux (Debian/Ubuntu-based systems)
sh sudo apt update && sudo apt upgrade -y sudo apt install -y python3-pip pip3 install rnsOn Raspberry Pi or ARM-based Systems
sh pip3 install rnsOn Windows
Using Windows Subsystem for Linux (WSL) or Python:
sh pip install rnsOn macOS
sh pip3 install rns
2. Configuring Reticulum
Once installed, Reticulum needs a configuration file. The default location is:
sh ~/.config/reticulum/config.tomlTo generate the default configuration:
sh rnsdThis creates a configuration file with default settings.
3. Using Reticulum
Starting the Reticulum Daemon
To run the Reticulum daemon (
rnsd), use:
sh rnsdThis starts the network stack, allowing applications to communicate over Reticulum.Testing Your Reticulum Node
Run the diagnostic tool to ensure your node is functioning:
sh rnstatusThis shows the status of all connected interfaces and peers.
4. Adding Interfaces
LoRa Interface (for Off-Grid Communications)
Reticulum supports long-range LoRa radios like the RAK Wireless and Meshtastic devices. To add a LoRa interface, edit
config.tomland add:
toml [[interfaces]] type = "LoRa" name = "My_LoRa_Interface" frequency = 868.0 bandwidth = 125 spreading_factor = 9Restart Reticulum to apply the changes.Serial (For Direct Device-to-Device Links)
For communication over serial links (e.g., between two Raspberry Pis):
toml [[interfaces]] type = "Serial" port = "/dev/ttyUSB0" baudrate = 115200TCP/IP (For Internet-Based Nodes)
If you want to bridge your Reticulum node over an existing IP network:
toml [[interfaces]] type = "TCP" listen = true bind = "0.0.0.0" port = 4242
5. Applications Using Reticulum
LXMF (LoRa Mesh Messaging Framework)
LXMF is a delay-tolerant, fully decentralized messaging system that operates over Reticulum. It allows encrypted, store-and-forward messaging without requiring an always-online server.
To install:
sh pip3 install lxmfTo start the LXMF node:
sh lxmfdNomad Network (Decentralized Chat & File Sharing)
Nomad is a Reticulum-based chat and file-sharing platform, ideal for off-grid communication.
To install:
sh pip3 install nomad-networkTo run:
sh nomadMesh Networking with Meshtastic & Reticulum
Reticulum can work alongside Meshtastic for true decentralized long-range communication.
To set up a Meshtastic bridge:
toml [[interfaces]] type = "LoRa" port = "/dev/ttyUSB0" baudrate = 115200
6. Security & Privacy Features
- Automatic End-to-End Encryption – Every message is encrypted by default.
- No Centralized Logging – Communication leaves no metadata traces.
- Self-Healing Routing – Designed to work in unstable or hostile environments.
7. Practical Use Cases
- Off-Grid Communication – Works in remote areas without cellular service.
- Censorship Resistance – Cannot be blocked by ISPs or governments.
- Emergency Networks – Enables resilient communication during disasters.
- Private P2P Networks – Create a secure, encrypted communication layer.
8. Further Exploration & Documentation
- Reticulum Official Manual: https://markqvist.github.io/Reticulum/manual/
- Reticulum GitHub Repository: https://github.com/markqvist/Reticulum
- Nomad Network: https://github.com/markqvist/NomadNet
- Meshtastic + Reticulum: https://meshtastic.org
Connections (Links to Other Notes)
- Mesh Networking for Decentralized Communication
- LoRa and Off-Grid Bitcoin Transactions
- Censorship-Resistant Communication Using Nostr & Reticulum
Tags
Reticulum #DecentralizedComms #MeshNetworking #CensorshipResistance #LoRa
Donations via
- Bitcoin Lightning: lightninglayerhash@getalby.com
-
 @ 43baaf0c:d193e34c
2025-03-06 21:38:10
@ 43baaf0c:d193e34c
2025-03-06 21:38:10From Bangkok to Las Palmas de Gran Canaria.

For the past three years, I’ve traveled from Bangkok to Las Palmas de Gran Canaria, with a stop in Dubai a 24-hour journey that brings me back to Europe and to my artist friend, Alecs Navio. Along with his wife, he runs a coworking space called Soppa de Azul.
The main reason I return here is to create new art. Alecs constantly inspires me—we talk about art, artists, and he shares books that spark new ideas for my work. As an artist, I believe it’s essential to keep evolving. Growth comes from inspiration, and there’s no better source than fellow artists. Surrounding yourself with creative minds fuels your passion, and it all starts with conversations about art and life.
 Today was a perfect example of why I’m here. I looked at some of my older artwork hanging in the coworking space and said I didn’t like it anymore. Alecs reminded me that I should appreciate my past work because it’s part of my journey. Without it I wouldn’t be the artist I am today.
Today was a perfect example of why I’m here. I looked at some of my older artwork hanging in the coworking space and said I didn’t like it anymore. Alecs reminded me that I should appreciate my past work because it’s part of my journey. Without it I wouldn’t be the artist I am today.I always say the journey is the destination, and Alecs helped me see that this applies to art as well. This is why I believe in surrounding myself with people who inspire me those who celebrate my growth and remind me why they are such an important part of my journey.
-
 @ 0c503f08:4aed05c7
2025-03-06 21:28:16
@ 0c503f08:4aed05c7
2025-03-06 21:28:16My host is Debian and I'm using VirtualBox. Everything seems to be working well.
originally posted at https://stacker.news/items/906016
-
 @ d6c48950:54d57756
2025-03-06 21:20:45
@ d6c48950:54d57756
2025-03-06 21:20:45I wanted to write my system for bitcoin inheritance and seed storage that will likely outlive me - the reason why is recently bitkey (squares hardware wallet) announced their inheritance system which is a vast improvement but still has a single point of failure square and the app they maintain though this is still a good thing and will improve the ecosystem and raise awareness there is a cheaper method that is just a secure but doesn’t have a single point of failure.
2/3 seed storage
2/3 seed storage is actually a pretty simple way of splitting up a key into three parts, if you have one part it’s useless, if you have any two parts it’s complete - if one piece is destroyed it doesn’t matter (demo below)
| A
| B
| C
| |-----|-----|-----| | 1. apple
| 2. zipper
| 3. dog
| | 4. tree
| 5. car
| 6. bus
| | 7. banana
| 8. motorbike
| 9. dune
| | 10. frank
| 11. foundation
| 12. meditation
| | 13. whiteboard
| 14. laptop
| 15. books
| | 16. perfume
| 17. computer
| 18. stone
| | 19. brick
| 20. spreadsheet
| 21. bird
| | 22. blog
| 23. leaves
| 24. grass
|This is a seed phrase split up into three parts (a,b,c) - now you can create your 3 parts
(1) | A
| B
| | |-----|-----|-----| | 1. apple
| 2. zipper
| | | 4. tree
| 5. car
| | | 7. banana
| 8. motorbike
| | | 10. frank
| 11. foundation
| | | 13. whiteboard
| 14. laptop
| | | 16. perfume
| 17. computer
| | | 19. brick
| 20. spreadsheet
| | | 22. blog
| 23. leaves
| |(2) | | B
| C
| |-----|-----|-----| | | 2. zipper
| 3. dog
| | | 5. car
| 6. bus
| | | 8. motorbike
| 9. dune
| | | 11. foundation
| 12. meditation
| | | 14. laptop
| 15. books
| | | 17. computer
| 18. stone
| | | 20. spreadsheet
| 21. bird
| | | 23. leaves
| 24. grass
|(3) | A
| | C
| |-----|-----|-----| | 1. apple
| | 3. dog
| | 4. tree
| | 6. bus
| | 7. banana
| | 9. dune
| | 10. frank
| | 12. meditation
| | 13. whiteboard
| | 15. books
| | 16. perfume
| | 18. stone
| | 19. brick
| | 21. bird
| | 22. blog
| | 24. grass
|Now you have your parts, you need at least 2/3 for it to be useful.
distribution
Distribution is pretty simple, keep one part, give a part to whomever you want to be able to claim your bitcoin upon death, give a part to someone you trust (along with instructions to post it to the claimant upon your death).
failure
For this to fail either 1. Two out of three parts would have to be destroyed 2. The trusted party would have to not post it AND either your part or the claimants would have to be destroyed 3. The trusted party cannot figure out how to use a seed phrase (by default you should include instructions i.e NEVER SHARE THE SEED, transfer to a recommended wallet from bitcoin.org then transfer to an exchange and sell)
-
 @ 43baaf0c:d193e34c
2025-03-06 20:55:27
@ 43baaf0c:d193e34c
2025-03-06 20:55:27Bangkok art city.
 Bangkok is a highly creative city, which is one of the reasons I love living here. I’d love to hold a second exhibition something special and even bigger than before. The fact that all major galleries are free to the public says a lot about how much Bangkok values art.
Bangkok is a highly creative city, which is one of the reasons I love living here. I’d love to hold a second exhibition something special and even bigger than before. The fact that all major galleries are free to the public says a lot about how much Bangkok values art.Over the last five months, I’ve been developing BangPOP art as both a concept and a blueprint for exhibitions worldwide. It serves as a guideline to ensure recognizable elements in each exhibition or event. While the artwork itself will always be unique, the POP Up exhibitions will have a distinct and recognizable identity wherever they take place.

You can read here the https://bitpopart.com/bangpop POP exhibition blue print.

Unfortunately, my plan to hold an exhibition at River City in Bangkok doesn’t seem to be coming together. Here’s the curator’s note:
‘our exhibition schedule on the 2nd floor this year and next year are quite packed and we have received numerous proposals at this moment.‘
 After considering alternative venues in Bangkok, I’m optimistic about finding the right fit. For now, my focus is shifting to Europe, where I’ll use the BangPOP blueprint as my guiding framework.
After considering alternative venues in Bangkok, I’m optimistic about finding the right fit. For now, my focus is shifting to Europe, where I’ll use the BangPOP blueprint as my guiding framework.

 Thank you Bangkok!
Thank you Bangkok!

-
 @ 878dff7c:037d18bc
2025-03-06 20:17:07
@ 878dff7c:037d18bc
2025-03-06 20:17:07Cyclone Alfred's Approach Prompts Widespread Preparations in Queensland
Summary:
Cyclone Alfred's anticipated landfall near Brisbane has led to extensive precautionary measures across Queensland. Authorities have advised residents to fill bathtubs to ensure water availability in case of supply disruptions. Additional recommendations include securing outdoor items, preparing emergency kits, and verifying insurance documentation, as damages are expected to be substantial. The cyclone's impact could affect up to 1.8 million homes, with potential wind gusts reaching 150 km/h. Residents are urged to stay updated through official channels and prioritize safety during this severe weather event.
Sources: News.com.au - 7 March 2025, The Courier-Mail - 6 March 2025
Doubts Emerge Over Australia's Acquisition of Aukus Nuclear Submarines
Summary:
Australia's plan to acquire nuclear-powered submarines under the Aukus agreement faces significant uncertainties. Concerns have arisen regarding the U.S.'s capacity to produce these submarines and its willingness to transfer control to Australia. Experts highlight challenges in the U.S. shipbuilding industry and suggest alternatives, such as revisiting deals with France, to ensure Australia's defense capabilities. Sources: The Guardian - March 7, 2025
Commonwealth Bank to Cut Jobs Amid Technology Restructuring
Summary:
The Commonwealth Bank of Australia (CBA) is set to cut approximately 150 jobs from its Sydney operations, with additional cuts affecting Melbourne, Brisbane, Perth, Hobart, and Tweed Heads. The Finance Sector Union criticizes the move, noting a contradiction between the bank's commitment to digital talent and the job cuts from its technology division. The bank claims the layoffs are necessary to facilitate faster digital customer experiences requiring enhanced skills.
Sources: News.com.au - March 7, 2025
Country Road Owner Warns of Ongoing Retail Recession in Australia
Summary:
Woolworths Holdings, owner of Country Road Group, reports a severe decline in sales and earnings, attributing it to a nearly two-year retail recession in Australia. The company cites over 700 business bankruptcies in 2024, low GDP growth, persistent inflation, and high interest rates as factors dampening consumer sentiment. Despite these challenges, some national retailers like JB Hi-Fi and Harvey Norman continue to thrive, highlighting a divide between retail "winners and losers."
Sources: The Australian - March 7, 2025
Calls to Enhance Australia's Drone and Missile Capabilities
Summary:
Australia's defense posture is under scrutiny following recent Chinese maritime activities. Experts advocate for increased investment in drone and missile technologies, citing their cost-effectiveness and proven efficacy in conflicts like Ukraine's. Despite being a leader in drone and radar technology, Australia's defense spending remains heavily focused on nuclear submarines. There's a growing call for strategic investment in domestic defense technologies to bolster military capabilities and industrial strength, ensuring the nation can meet global defense commitments and technological advancements.
Sources: The Australian - March 7, 2025
Australia's Visa Cancellation of Controversial Preacher
Summary:
Australia's Department of Home Affairs has canceled the visa of Hussain Makke, a Lebanese-based social media figure who praised Hezbollah leader Hassan Nasrallah as the "world's greatest freedom fighter." Makke had planned to speak at events in Sydney and Melbourne during Ramadan. This decision underscores Australia's stance against individuals who glorify terrorism, especially amid rising concerns over antisemitism. Authorities emphasize that endorsing terrorist organizations contradicts Australian values, and such individuals are unwelcome in the country.
Sources: The Daily Telegraph - March 7, 2025
Activists Target Tesla in Protests Against USA Federal Job Cuts
Summary:
Activists have initiated "Tesla Takedown" protests, targeting Tesla dealerships to oppose job cuts in the federal workforce overseen by Elon Musk, appointed by President Trump to lead the Department of Government Efficiency. Demonstrators aim to tarnish the Tesla brand, urging consumers to boycott the company's products.
Sources: Reuters - March 6, 2025
Switzerland Cancels Geneva Conventions Meeting on Palestinian Territories
Summary:
Switzerland has canceled a conference scheduled for March 7, intended to discuss the application of the Geneva Conventions in the occupied Palestinian territories, due to insufficient support from participating countries. The Palestinian envoy expressed disappointment, stating the draft declaration did not meet expectations, while Israel had criticized the planned meeting.
Sources: Reuters - March 6, 2025
Comprehensive Reforms Proposed for Handling Sexual Violence Cases
Summary:
The Australian Law Reform Commission (ALRC) has released a report recommending significant changes to improve the treatment of sexual violence victims within the criminal justice system. Key proposals include allowing victims to provide evidence through prerecorded hearings, offering government-funded legal representation, and creating "trauma-informed" environments during police interviews. The report also advocates for national consistency in defining consent and the adoption of restorative justice practices. In response, the Albanese government has announced a $21.4 million funding package to support these initiatives, aiming to reduce systemic barriers that deter 92% of women from reporting sexual violence.
Sources: The Australian - 7 March 2025, News.com.au - 7 March 2025, The Guardian - 7 March 2025
Surge in Cosmetic Injectables Raises Health Concerns
Summary:
Australia's cosmetic injectables industry is under scrutiny following incidents of unqualified practitioners performing invasive procedures, leading to severe health risks such as exposure to bloodborne viruses. Medical professionals are calling for stricter regulations and enforcement to safeguard public health.
Sources: The Australian - 7 March 2025
China's Spring Festival Gala Showcases Advancements in Humanoid Robotics
Summary:
During China’s 2025 Spring Festival Gala, a notable display of the country’s advancements in robotics was showcased through a dance performance featuring 16 humanoid robots developed by Hangzhou Yushu (Unitree). The robots performed the Yangko folk dance alongside human dancers, demonstrating precision and coordination. This event highlighted China's focus on robotics as part of a broader trend, with major tech companies like Tesla and Nvidia also prioritizing humanoid robots. China's Ministry of Industry and Information Technology has set ambitious goals to mass-produce advanced humanoid robots by 2025.
Sources: Business Insider - March 7, 2025
Environment Minister Approves Three NSW Wind Farms Amid Controversy
Summary:
Environment Minister Tanya Plibersek has approved three wind farm projects in New South Wales: Hills of Gold near Nundle, Spicers Creek northwest of Gulgong, and amendments to the Liverpool Range project near Coolah. These projects, facing opposition due to environmental and infrastructure concerns, are expected to create 1,340 construction jobs and 80 ongoing positions. Critics plan legal challenges, citing potential impacts on biodiversity and local infrastructure. The approvals include strict environmental conditions, though significant habitat clearing will occur. To date, the federal government has approved 77 renewable energy projects, capable of powering over 10 million homes.
Sources: The Australian - 7 March 2025
-
 @ a296b972:e5a7a2e8
2025-03-06 19:55:59
@ a296b972:e5a7a2e8
2025-03-06 19:55:59Die Kinder einer Grundschule sollten im Herbst 2024 einen Aufsatz über die amtierende deutsche Außenministerin schreiben. Hier das Ergebnis des 12-jährigen Michaels, wie ihn eine Grundschullehrerin eingesandt haben könnte:
„Die Tante in Berlin hat immer eine schöne Haarfrisur und trägt immer schicke Sachen. Wenn sie mit dem Regierungsflieger unterwegs ist (oft klappt das aber nicht richtig, weiß nicht warum), dann knittern ihre Kleider bestimmt überhaupt nicht. Da hat sie es gut, meine Mama bügelt gar nicht gerne.
Auch hat sie eine Hilfe, die ihr Gesicht immer anmalt und ihr die Haare schön macht. Die bekommt wohl einen Haufen Geld dafür, was aus den Steuern abgezweigt wird, die mein Papa, der sehr fleißig arbeitet, bezahlt.
Die Tante, die mir eher wie ein Mädchen in meinem Alter vorkommt, erinnert mich immer an die Lisa aus der Nachbarklasse, die so frech ist, dass ich und andere ihr manchmal an den Haaren ziehen müssen, damit sie wieder vernünftig wird.
Wenn man ihr sagt, sie ist doof, dann wirft sie den Kopf in den Nacken und zieht beleidigt ab.
Überhaupt benimmt sie sich oft, wie eine beleidigte Leberwurst. Und wenn andere was sagen, was ihr nicht passt, wird sie frech. Ich habe gelernt, dass man möglichst nicht frech sein soll.
Ich bin froh, dass sie keinen roten Knopf hat, auf den sie drücken könnte, nur, um mal zu sehen, was dann passiert.
Alle Elefanten auf der Welt sind böse auf sie, weil sie Porzellan viel besser zerdeppern kann, als sie selber.
Mein Papa sagt, dass zu ihrem Beruf zählt, dass man mit den Leuten redet, bevor man Geld gibt, um auf sie zu schießen, aber das kann sie wohl nicht. Was sie wohl tun müsste, wäre Diplomatie (ich bin ehrlich, dass hab ich von Andreas abgeschrieben, der kennt solche Fremdwörter).
Gut gefallen hat mir ihre Einladung zum Kindergeburtstag im Auswärtigen Amt, wo im vergangenen Sommer alle Türen offen waren. Da wurden auch so lustige Videos gedreht, wo so Leute aus dem Fahrstuhl kommen, die so glitzernde Decken umhatten und tanzten.
Mit ihren oft lustigen Sätzen kitzelt sie wichtige Erwachsene von großen Ländern, ohne sie dabei anfassen zu müssen, das würde ich auch gerne können. Ich wüsste schon, wen ich gerne mal so richtig Auskitzeln wollte.
Ganz oft benutzt sie das Wort „Brutaler Angriffskrieg“ und soweit ich das schon verstehe, sagt sie oft Sachen, die gar keinen Sinn ergeben. Meine Lehrerin sagt immer zu uns, wir sollen lieber den Mund halten, wenn wir nicht genau wissen, was wir sagen wollen. Besser sei es, vor dem Reden das Gehirn einzuschalten. Das sehe ich ein und ich bemühe mich wirklich darum. Ich glaube, sie vergisst das manchmal.
Wenn sie mal nicht weiterweiß, kann sie bestimmt noch den Onkel Klaus vom WEF fragen, bei dem sie Politikerin gelernt hat.
Wenn sie mal nicht mehr so feministisch arbeiten kann oder will, könnte sie vielleicht Kindergärtnerin werden, aber ich glaube, kein Kind könnte sie leiden, weil sie immer so altklug und bockig tut, und das können wir Kinder gar nicht leiden. Und eigentlich soll man ja nicht von einem Beruf, den man nicht kann, in einen anderen Beruf wechseln, den man auch nicht kann.
Schön finde ich, dass die ganze Welt über sie lacht, wo doch alles im Moment so traurig ist und alle von Krieg reden und Bedrohung und dass Deutschland wieder kriegstüchtig werden soll. Das macht mir Angst. Da habe ich oft das Gefühl, alle Erwachsenen sind verrückt geworden und benehmen sich nur noch so, wie ich, als ich 8 Jahre alt war. Ich weiß noch, da habe ich ziemlich viel Blödsinn gemacht, aber jetzt bin ich schon viel vernünftiger geworden.
Mein Pausenbrot würde ich nicht mit ihr tauschen, weil ich sie nicht leiden kann, denn sie benimmt sich oft wie die Lisa, und die ist echt eine richtig doofe Ziege.
Weil ich sie nicht mag, wünsche ich mir, dass sie bald nicht mehr im Fernsehen zu sehen ist. Dann kann sie auch ihre Anziehsachen wieder selber bügeln, wie meine Mama.“
(Manche Wünsche gehen in Erfüllung!)
-
 @ f3873798:24b3f2f3
2025-03-06 19:21:36
@ f3873798:24b3f2f3
2025-03-06 19:21:36Olá pessoal!
Estas altas temperaturas mais períodos de chuvas, é um prato cheio para a proliferação de mosquitos o que além de ser um incomodo pode ser tornar questão de saúde pública devido as doenças trazidas por eles.
Por isso trouxe para vocês uma receitinha para espantar os mosquitos da sua casa.
Bora lá
Receita Espanta mosquito
Ingredientes:
500 mL de álcool de cereais ou álcool 70 % 10g de cravo-da-índia. 10 gotas de óleo essencial de citronela 10 gotas de óleo essencial de lavanda 1 borrifador
Modo de preparo
-
Coloque os cravos-da-índia dentro de um frasco com álcool de cereais.
-
Deixe a mistura descansar por pelo menos 24 horas, agitando de vez em quando.
-
Após esse período, coe os cravos e adicione os óleos essenciais de citronela e lavanda.
-
Despeje o líquido em um borrifador e aplique nos cômodos da casa, especialmente perto de janelas e portas.
E Adeus mosquitos 😎
-
-
 @ 27c04be0:af374d05
2025-03-06 19:10:10
@ 27c04be0:af374d05
2025-03-06 19:10:10Your wedding day is all about celebrating your unique style—and that includes the car you arrive in! Whether you’re planning a cozy barn wedding, a sparkling glam affair, or a sleek minimalist ceremony, the right wedding car hire Walthamstow can make your big day even more special. But how do you pick a car that matches your theme?
Don’t worry—we’ll break it down in simple terms! In this guide, you’ll learn how to match car styles to rustic, glam, or minimalist weddings, with easy tips and examples. Let’s get started!
Visit us> Wedding Car Hire Service Near You
** 1. Rustic Weddings: Charming & Natural Vibes ** Rustic weddings are all about relaxed, earthy vibes—think barns, gardens, or countryside venues. Your wedding car hire Walthamstow should feel cozy, vintage, and a little bit nostalgic.
** Best Car Styles for Rustic Weddings
**Vintage Cars:
Example: A 1960s Volkswagen Camper Van or a classic Ford pickup truck.
Why it works: Retro designs match the "old-world" charm of rustic décor.Horse-Drawn Carriages:
Example: A wooden carriage with floral decorations.
Why it works: Adds fairy-tale magic to outdoor settings.**Convertible Classic Cars: ** Example: A 1950s Chevrolet Bel Air with a soft-top roof.
Why it works: Perfect for sunny countryside drives.**Styling Tips ** Add wildflowers, twine, or lace to the car’s exterior.
Use wooden signs like “Just Married” on the back.
Choose neutral colors (cream, sage green, or rusty red).Pro Tip: Ask your wedding car hire Walthamstow Company if they offer vintage or rustic-themed vehicles. Many specialize in these styles!
** 2. Glam Weddings: Luxurious & Sparkly Vibes ** Glam weddings are bold, elegant, and full of sparkle—think chandeliers, sequins, and grand ballrooms. Your wedding car hire should scream luxury and sophistication.
** Best Car Styles for Glam Weddings ** Luxury Sedans:
Example: Rolls Royce Phantom or Mercedes-Benz S-Class.
Why it works: Sleek, shiny, and timeless.Stretch Limousines:
Example: A black or white limo with tinted windows.
Why it works: Plenty of space for the bridal party and champagne toasts!**Vintage Luxury Cars: ** Example: A 1930s Bentley with polished chrome details.
Why it works: Combines old Hollywood glam with modern comfort.** Styling Tips**
Add satin ribbons, crystal decorations, or a red carpet rollout.
Choose metallic colors (silver, gold, or rose gold accents).
Pair with a chauffeur in formal attire (think suits or gloves).Pro Tip: Many wedding car hire Walthamstow services offer “glam packages” with extras like champagne, flower petals, or photo backdrops.
3. Minimalist Weddings: Simple & Modern Vibes
Minimalist weddings focus on clean lines, neutral colors, and “less is more” elegance. Your wedding car hire should be sleek, modern, and fuss-free.Best Car Styles for Minimalist Weddings
Modern Electric Cars:
Example: Tesla Model S or Audi e-tron.
Why it works: Eco-friendly and stylish.Convertible Sports Cars:
Example: Porsche 911 or Jaguar F-Type.
Why it works: Sharp design matches minimalist aesthetics.Understated Luxury Cars:
Example: BMW 7 Series or Lexus LS.
Why it works: Simple elegance without extra frills.Styling Tips
Keep decorations minimal (e.g., a single white ribbon or geometric shapes).
Stick to neutral colors (white, black, or gray).
Opt for matte finishes instead of glossy paint.Pro Tip: Ask your wedding car hire provider for cars with “clean” designs—no flashy logos or busy patterns.
How to Choose the Right Wedding Car Hire Walthamstow Service
Finding the perfect car is easier when you know what to ask!Questions to Ask
**“Do you have cars that fit rustic/glam/minimalist themes?” ** “Can I see photos of your vehicles?”
“Do you offer decorations or styling add-ons?”Budget Tips
Book early for discounts (popular cars sell fast!).
Share your wedding theme—some companies offer package deals.Keyword Alert: Always confirm your wedding car hire includes insurance, a chauffeur, and setup time.
Mistakes to Avoid
Ignoring the venue: A huge limo won’t fit a narrow countryside road.
Forgetting the weather: Convertibles are risky for rainy days!
Last-minute bookings: The best wedding car hire options get booked months ahead.Bottom Line
Your wedding car isn’t just a ride—it’s part of your story! For rustic weddings, go vintage and cozy. For glam weddings, pick something shiny and luxurious. For minimalist weddings, choose sleek and modern. No matter your style, the right wedding car hire Walthamstow will make your entrance unforgettable.So, dream big, plan ahead, and roll up in a car that’s as unique as your love!
FAQs About Wedding Car Hire
-
How do I pick the right car for a rustic wedding?
Look for vintage or retro vehicles like a Volkswagen Camper Van or a classic pickup truck.
Ask your Wedding Car Hire company if they offer floral decorations or wooden accents to match barn/outdoor venues. -
What’s the average cost of glam Wedding Car Hire?
Luxury cars (e.g., Rolls Royce) or limos range from $500–$1,500+ depending on duration and add-ons (like champagne or red carpets). -
Can I decorate the car myself?
Yes, but check with your Wedding Car Hire provider first. Some restrict adhesives or paints that could damage the vehicle. -
How early should I book my Wedding Car Hire?
6–12 months in advance, especially for peak seasons (summer, holidays) or popular cars like vintage models. -
Are chauffeurs included in Wedding Car Hire packages?
Most companies include a professional driver, but confirm during booking. They’ll ensure timely arrivals and handle parking. -
What if my Wedding Car Hire breaks down on the day?
Reputable services offer backup vehicles. Always ask about their emergency plan before signing a contract. -
Can I rent eco-friendly cars for a minimalist wedding?
Yes! Many Wedding Car Hire companies now offer Teslas, Audis, or hybrids for sleek, sustainable arrivals. -
How do I match the car to my venue’s style?
Rustic: Choose vintage cars for barns or gardens.
Glam: Opt for limos or luxury sedans for ballrooms.
Minimalist: Pick modern, clean designs for urban venues. -
Are there extra fees for Wedding Car Hire?
Watch for mileage limits, overtime charges, or decor add-ons. Read the contract carefully to avoid surprises. -
Can I rent multiple cars for the wedding party?
Yes! Many Wedding Car Hire providers offer group packages (e.g., one car for the couple, others for bridesmaids or family). -
What’s the best car color for a minimalist wedding?
Stick to neutrals like white, black, or matte gray. Avoid flashy colors or patterns. -
Do Wedding Car Hire services offer insurance?
Most do, but confirm coverage details (e.g., damage, cancellations) before booking.
-
-
 @ 15a592c4:e8bdd024
2025-03-06 18:59:13
@ 15a592c4:e8bdd024
2025-03-06 18:59:13"Suffering has been stronger than all other teaching, and has taught me to understand what your heart used to be. I have been bent and broken, but – I hope – into a better shape." – Charles Dickens
Suffering is an inevitable part of life, and it can be a transformative experience that teaches us valuable lessons. While it's natural to try to avoid pain and hardship, embracing suffering as a teacher can help us grow, learn, and rise above our challenges. In this article, we'll explore the lessons that only suffering can teach.
Lesson; 1. Resilience and Adaptability Suffering teaches us to be resilient and adaptable in the face of adversity. When we're forced to navigate difficult circumstances, we learn to adjust our expectations, priorities, and strategies. This adaptability helps us develop coping mechanisms and bounce back from setbacks.
2: Empathy and Compassion Suffering gives us a deeper understanding of others who are struggling. When we've experienced pain and hardship ourselves, we're more likely to empathize with others who are going through similar challenges. This empathy fosters compassion, kindness, and a stronger sense of community.
3: Gratitude and Appreciation Suffering helps us appreciate the good things in life and cultivate gratitude. When we've faced hardship, we're more likely to cherish the people, experiences, and moments that bring us joy. This gratitude shifts our focus from what's lacking to what we already have.
4: Self-Awareness and Introspection Suffering prompts us to look inward and confront our own strengths, weaknesses, and motivations. Through introspection, we gain a deeper understanding of ourselves, our values, and our goals. This self-awareness helps us make positive changes and grow as individuals.
5: Hope and Perseverance Suffering teaches us to hold onto hope, even in the darkest moments. When we've faced adversity and come out the other side, we develop a sense of perseverance that helps us push through challenges. This hope and perseverance give us the strength to keep moving forward, even when the road ahead seems uncertain.
Conclusion Suffering is an inevitable part of life, but it can also be a transformative teacher. By embracing the lessons that suffering can teach us, we can rise above our challenges, grow as individuals, and develop the resilience, empathy, gratitude, self-awareness, and hope that we need to navigate life's ups and downs.
-
 @ 15a592c4:e8bdd024
2025-03-06 18:51:27
@ 15a592c4:e8bdd024
2025-03-06 18:51:27Strategies for Effective Time Management and Productivity
In today's fast-paced world, managing time effectively is crucial for achieving success in both personal and professional life. With numerous tasks competing for our attention, it's easy to get bogged down and lose focus. However, by implementing the right strategies, you can optimize your time management skills, boost productivity, and accomplish your goals.
Set Clear Goals
Before you can manage your time effectively, you need to know what you want to achieve. Setting clear goals helps you focus on what's truly important and allocate your time accordingly. Try to set SMART (Specific, Measurable, Achievable, Relevant, and Time-bound) goals that align with your priorities.
Use a Scheduling Tool
A scheduling tool, such as a planner, calendar, or app, helps you organize your tasks, appointments, and deadlines. Write down all your tasks, big and small, and allocate specific time slots for each. Set reminders and notifications to ensure you stay on track.
Prioritize Tasks
Not all tasks are created equal. Prioritize tasks based on their urgency and importance. Use the Eisenhower Matrix to categorize tasks into four quadrants:
- Urgent and important (Do first)
- Important but not urgent (Schedule)
- Urgent but not important (Delegate)
- Not urgent or important (Eliminate)
Avoid Multitasking
Multitasking may seem like an efficient way to get things done, but it can actually decrease productivity and increase stress. Focus on one task at a time, and give it your undivided attention.
Manage Distractions
Distractions are everywhere, from social media to email notifications. Identify your most significant distractions and eliminate them while you work. Use tools like website blockers or apps that help you stay focused.
Take Breaks
Taking regular breaks can help you recharge and maintain productivity. Use the Pomodoro Technique: work for 25 minutes, take a 5-minute break, and repeat.
Learn to Say No
Don't take on too much by trying to please everyone. Learn to say no to tasks that don't align with your goals or values. Remember, saying no to something that doesn't serve you means saying yes to yourself.
Review and Adjust
Regularly review your time management strategy to identify areas for improvement. Adjust your schedule, goals, and habits as needed.
Effective time management and productivity require discipline, intention, and strategy. By implementing these strategies, you'll be able to:
- Achieve your goals
- Reduce stress and anxiety
- Increase productivity and efficiency
- Enjoy a better work-life balance
Remember, time management is a skill that takes practice, so be patient and persistent. With the right strategies and mindset, you can master your time and unlock your potentials...
-
 @ 97c70a44:ad98e322
2025-03-06 18:38:10
@ 97c70a44:ad98e322
2025-03-06 18:38:10When developing on nostr, normally it's enough to read the NIP related to a given feature you want to build to know what has to be done. But there are some aspects of nostr development that aren't so straightforward because they depend less on specific data formats than on how different concepts are combined.
An example of this is how for a while it was considered best practice to re-publish notes when replying to them. This practice emerged before the outbox model gained traction, and was a hacky way of attempting to ensure relays had the full context required for a given note. Over time though, pubkey hints emerged as a better way to ensure other clients could find required context.
Another one of these things is "relay-based groups", or as I prefer to call it "relays-as-groups" (RAG). Such a thing doesn't really exist - there's no spec for it (although some aspects of the concept are included in NIP 29), but at the same time there are two concrete implementations (Flotilla and Chachi) which leverage several different NIPs in order to create a cohesive system for groups on nostr.
This composability is one of the neat qualities of nostr. Not only would it be unhelpful to specify how different parts of the protocol should work together, it would be impossible because of the number of possible combinations possible just from applying a little bit of common sense to the NIPs repo. No one said it was ok to put
ttags on akind 0. But no one's stopping you! And the semantics are basically self-evident if you understand its component parts.So, instead of writing a NIP that sets relay-based groups in stone, I'm writing this guide in order to document how I've combined different parts of the nostr protocol to create a compelling architecture for groups.
Relays
Relays already have a canonical identity, which is the relay's url. Events posted to a relay can be thought of as "posted to that group". This means that every relay is already a group. All nostr notes have already been posted to one or more groups.
One common objection to this structure is that identifying a group with a relay means that groups are dependent on the relay to continue hosting the group. In normal broadcast nostr (which forms organic permissionless groups based on user-centric social clustering), this is a very bad thing, because hosts are orthogonal to group identity. Communities are completely different. Communities actually need someone to enforce community boundaries, implement moderation, etc. Reliance on a host is a feature, not a bug (in contrast to NIP 29 groups, which tend to co-locate many groups on a single host, relays-as-groups tends to encourage one group, one host).
This doesn't mean that federation, mirrors, and migration can't be accomplished. In a sense, leaving this on the social layer is a good thing, because it adds friction to the dissolution/forking of a group. But the door is wide open to protocol additions to support those use cases for relay-based groups. One possible approach would be to follow this draft PR which specified a "federation" event relays could publish on their own behalf.
Relay keys
This draft PR to NIP 11 specifies a
selffield which represents the relay's identity. Using this, relays can publish events on their own behalf. Currently, thepubkeyfield sort of does the same thing, but is overloaded as a contact field for the owner of the relay.AUTH
Relays can control access using NIP 42 AUTH. There are any number of modes a relay can operate in:
-
No auth, fully public - anyone can read/write to the group.
-
Relays may enforce broad or granular access controls with AUTH.
Relays may deny EVENTs or REQs depending on user identity. Messages returned in AUTH, CLOSED, or OK messages should be human readable. It's crucial that clients show these error messages to users. Here's how Flotilla handles failed AUTH and denied event publishing:
LIMITS could also be used in theory to help clients adapt their interface depending on user abilities and relay policy.
- AUTH with implicit access controls.
In this mode, relays may exclude matching events from REQs if the user does not have permission to view them. This can be useful for multi-use relays that host hidden rooms. This mode should be used with caution, because it can result in confusion for the end user.
See Triflector for a relay implementation that supports some of these auth policies.
Invite codes
If a user doesn't have access to a relay, they can request access using this draft NIP. This is true whether access has been explicitly or implicitly denied (although users will have to know that they should use an invite code to request access).
The above referenced NIP also contains a mechanism for users to request an invite code that they can share with other users.
The policy for these invite codes is entirely up to the relay. They may be single-use, multi-use, or require additional verification. Additional requirements can be communicated to the user in the OK message, for example directions to visit an external URL to register.
See Triflector for a relay implementation that supports invite codes.
Content
Any kind of event can be published to a relay being treated as a group, unless rejected by the relay implementation. In particular, NIP 7D was added to support basic threads, and NIP C7 for chat messages.
Since which relay an event came from determines which group it was posted to, clients need to have a mechanism for keeping track of which relay they received an event from, and should not broadcast events to other relays (unless intending to cross-post the content).
Rooms
Rooms follow NIP 29. I wish NIP 29 wasn't called "relay based groups", which is very confusing when talking about "relays as groups". It's much better to think of them as sub-groups, or as Flotilla calls them, "rooms".
Rooms have two modes - managed and unmanaged. Managed rooms follow all the rules laid out in NIP 29 about metadata published by the relay and user membership. In either case, rooms are represented by a random room id, and are posted to by including the id in an event's
htag. This allows rooms to switch between managed and unmanaged modes without losing any content.Managed room names come from
kind 39000room meta events, but unmanaged rooms don't have these. Instead, room names should come from members' NIP 51kind 10009membership lists. Tags on these lists should look like this:["group", "groupid", "wss://group.example.com", "Cat lovers"]. If no name can be found for the room (i.e., there aren't any members), the room should be ignored by clients.Rooms present a difficulty for publishing to the relay as a whole, since content with an
htag can't be excluded from requests. Currently, relay-wide posts are h-tagged with_which works for "group" clients, but not more generally. I'm not sure how to solve this other than to ask relays to support negative filters.Cross-posting
The simplest way to cross-post content from one group (or room) to another, is to quote the original note in whatever event kind is appropriate. For example, a blog post might be quoted in a
kind 9to be cross-posted to chat, or in akind 11to be cross-posted to a thread.kind 16reposts can be used the same way if the reader's client renders reposts.Posting the original event to multiple relays-as-groups is trivial, since all you have to do is send the event to the relay. Posting to multiple rooms simultaneously by appending multiple
htags is however not recommended, since group relays/clients are incentivised to protect themselves from spam by rejecting events with multiplehtags (similar to how events with multiplettags are sometimes rejected).Privacy
Currently, it's recommended to include a NIP 70
-tag on content posted to relays-as-groups to discourage replication of relay-specific content across the network.Another slightly stronger approach would be for group relays to strip signatures in order to make events invalid (or at least deniable). For this approach to work, users would have to be able to signal that they trust relays to be honest. We could also use ZkSNARKS to validate signatures in bulk.
In any case, group posts should not be considered "private" in the same way E2EE groups might be. Relays-as-groups should be considered a good fit for low-stakes groups with many members (since trust deteriorates quickly as more people get involved).
Membership
There is currently no canonical member list published by relays (except for NIP 29 managed rooms). Instead, users keep track of their own relay and room memberships using
kind 10009lists. Relay-level memberships are represented by anrtag containing the relay url, and room-level memberships are represented using agrouptag.Users can choose to advertise their membership in a RAG by using unencrypted tags, or they may keep their membership private by using encrypted tags. Advertised memberships are useful for helping people find groups based on their social graph:

User memberships should not be trusted, since they can be published unilaterally by anyone, regardless of actual access. Possible improvements in this area would be the ability to provide proof of access:
- Relays could publish member lists (although this would sacrifice member privacy)
- Relays could support a new command that allows querying a particular member's access status
- Relays could provide a proof to the member that they could then choose to publish or not
Moderation
There are two parts to moderation: reporting and taking action based on these reports.
Reporting is already covered by NIP 56. Clients should be careful about encouraging users to post reports for illegal content under their own identity, since that can itself be illegal. Relays also should not serve reports to users, since that can be used to find rather than address objectionable content.
Reports are only one mechanism for flagging objectionable content. Relay operators and administrators can use whatever heuristics they like to identify and address objectionable content. This might be via automated policies that auto-ban based on reports from high-reputation people, a client that implements NIP 86 relay management API, or by some other admin interface.
There's currently no way for moderators of a given relay to be advertised, or for a moderator's client to know that the user is a moderator (so that they can enable UI elements for in-app moderation). This could be addressed via NIP 11, LIMITS, or some other mechanism in the future.
General best practices
In general, it's very important when developing a client to assume that the relay has no special support for any of the above features, instead treating all of this stuff as progressive enhancement.
For example, if a user enters an invite code, go ahead and send it to the relay using a
kind 28934event. If it's rejected, you know that it didn't work. But if it's accepted, you don't know that it worked - you only know that the relay allowed the user to publish that event. This is helpful, becaues it may imply that the user does indeed have access to the relay. But additional probing may be needed, and reliance on error messages down the road when something else fails unexpectedly is indispensable.This paradigm may drive some engineers nuts, because it's basically equivalent to coding your clients to reverse-engineer relay support for every feature you want to use. But this is true of nostr as a whole - anyone can put whatever weird stuff in an event and sign it. Clients have to be extremely compliant with Postell's law - doing their absolute best to accept whatever weird data or behavior shows up and handle failure in any situation. Sure, it's annoying, but it's the cost of permissionless development. What it gets us is a completely open-ended protocol, in which anything can be built, and in which every solution is tested by the market.
-
-
 @ 5b0183ab:a114563e
2025-03-06 17:38:10
@ 5b0183ab:a114563e
2025-03-06 17:38:10What Is Dark Nostr?
Dark Nostr can be described as the unintended adverse effects that arise from creating systems designed to resist censorship and promote freedom. These systems often rely on algorithms and micropayments to function, but their very design can inadvertently spawn phenomena that are unpredictable, uncontrollable, and sometimes downright weird.
Think of it as the Yin to the Yang of decentralized freedom—a necessary shadow cast by the bright ideals of liberation. While freedom protocols aim to empower individuals, they also open the door to consequences that aren’t always sunshine and rainbows.
An Emergent Phenomenon
The fascinating thing about Dark Nostr is its emergent nature. This means it’s not something you can fully define or predict ahead of time; instead, it arises organically as decentralized systems are implemented and evolve. Like watching clouds form shapes in the sky, GM miners panhandle for sats or shower girls in the global feed, you can only observe it as it happens—and even then, its contours remain elusive.
Emergent phenomena are tricky beasts. While simplicity is at the core of the protocol layer darkness is born on the edge where complexity thrives—where individual components interact in ways that produce unpredictable outcomes. In this case, Dark Nostr encapsulates everything from algorithmic quirks and micropayment dynamics to unforeseen social consequences within decentralized ecosystems.
Studying Dark Nostr: Memes as Cultural Artifacts
Here’s where things get anthropologically juicy: much of what we know about Dark Nostr comes not from academic papers or technical manuals but from memes. Yes, memes—the internet’s favorite medium for cultural commentary—have become a lens through which this phenomenon is being observed and studied.
Memes act as modern-day hieroglyphs, distilling complex ideas into bite-sized cultural artifacts that reflect collective sentiment. When communities encounter something as nebulous as Dark Nostr, they turn to humor and symbolism to make sense of it. In doing so, they create a shared narrative—a way to grapple with the shadow side of decentralization without losing sight of its promise.
Why Does It Matter?
Dark Nostr isn’t just an abstract concept for philosophers or tech enthusiasts—it’s a reminder that every innovation comes with trade-offs. While decentralized systems aim to empower individuals by resisting censorship and central control, they also carry risks that must be acknowledged:
- Algorithmic Chaos: Algorithms designed for freedom might amplify harmful content or create echo chambers.
- Micropayment Pitfalls: Financial incentives could lead to exploitation or manipulation within these systems.
- Social Dynamics: The lack of centralized control might enable bad actors or foster unforeseen societal shifts.Understanding Dark Nostr is crucial for anyone involved in building or using decentralized technologies. It challenges us to balance freedom with responsibility and reminds us that even the most well-intentioned systems have their shadow side.
Conclusion: Embracing the Shadow
Dark Nostr is more than just a cautionary tale—it’s a fascinating glimpse into the complexities of human interaction with technology. As an emergent phenomenon, it invites us to remain vigilant and adaptive as we navigate the uncharted waters of decentralization.
By studying its manifestations through cultural artifacts like memes and engaging in thoughtful reflection, we can better prepare for both its opportunities and risks. After all, every great innovation needs its shadow—it’s what makes progress real, messy, and human.
So here we stand before Dark Nostr: may we study it wisely, meme it relentlessly, and learn from its lessons as we build the future together.
Stay Vigilent Nostr.....
-
 @ 4925ea33:025410d8
2025-03-06 15:37:04
@ 4925ea33:025410d8
2025-03-06 15:37:04Os óleos essenciais são os principais ativos terapêuticos da Aromaterapia. No entanto, assim como qualquer substância que aplicamos na pele, inalamos ou ingerimos, eles podem causar reações alérgicas. Esse risco é ainda maior porque os óleos essenciais contêm compostos altamente concentrados, alguns dos quais possuem grande potencial alergênico. Por isso, é fundamental conhecer bem os óleos essenciais e entender seus riscos antes de utilizá-los.
Entendendo os riscos dos óleos essenciais

Embora sejam naturais, os óleos essenciais são altamente concentrados e podem provocar irritações ou alergias em algumas pessoas. Cada óleo contém diferentes componentes químicos, e é essencial compreender sua toxicidade para um uso seguro.
Podemos dividir os principais componentes químicos dos óleos essenciais em dois grandes grupos:
- Aromáticos ou fenóis
- Terpênicos
Além desses, existem outras substâncias que, apesar de terem propriedades terapêuticas, também podem apresentar riscos, como: lactonas, cumarinas (responsáveis pela fototoxicidade), ftalidas, compostos nitrogenados e compostos sulfurados.
A toxicidade de um óleo essencial depende da concentração dessas substâncias e do método de extração. Por exemplo, óleos obtidos pelo método de prensagem a frio preservam melhor seus componentes químicos, tornando-se mais potentes terapeuticamente, mas também mais propensos a causar reações adversas.
Os principais riscos dos óleos essenciais incluem:
✔️ Fotossensibilização (aumenta a sensibilidade da pele ao sol) ✔️ Efeito cáustico (pode causar queimaduras químicas) ✔️ Irritação na pele e nas mucosas ✔️ Reações alérgicas ✔️ Nefrotoxicidade (toxicidade para os rins) ✔️ Hepatotoxicidade (toxicidade para o fígado) ✔️ Neurotoxicidade (efeitos no sistema nervoso)
Diante desses riscos, é essencial contar com a orientação de um profissional e sempre realizar um teste de sensibilidade antes de usar qualquer óleo essencial.
Como fazer o teste de sensibilidade?

O teste de sensibilidade deve ser feito em áreas mais sensíveis da pele, como a dobra do cotovelo ou atrás da orelha – sendo a dobra do cotovelo a opção mais segura.
Passo a passo: Diluir o óleo essencial: misture 1 ou 2 gotas do óleo essencial em 5 mL de óleo carreador (ou siga a proporção de 1 gota de óleo essencial para 5 gotas de carreador). Aplicar na pele: passe a mistura na região escolhida. Observar por 24 horas: caso surjam vermelhidão, coceira ou irritação, é importante avaliar a gravidade da reação com um profissional antes de prosseguir com o uso. Mesmo em casos de reações leves, pode ser possível utilizar o óleo essencial com uma diluição maior. Nesses casos, o aromaterapeuta pode ajustar a formulação conforme tabelas específicas para pessoas sensíveis.
Dicas para um uso seguro dos óleos essenciais

✅ Nunca use óleos essenciais puros na pele. Sempre dilua em um óleo carreador adequado, pois ele transporta os ativos sem alterar suas propriedades e pode até potencializar os efeitos terapêuticos. ✅ Atenção à inalação! Ajuste o número de gotas no difusor e o tempo de exposição. No início do tratamento, prefira difusões curtas (até 30 minutos). ✅ Atenção às diluições! As proporções variam conforme o público:
Crianças e pessoas sensíveis: diluição máxima de 1% de óleo essencial na fórmula. Adultos saudáveis: diluição entre 2% e 3%.
Se você tem dúvidas ou quer saber como a Aromaterapia pode ajudar no seu dia a dia, me mande uma mensagem! Será um prazer te ajudar a usar os óleos essenciais com segurança. 😊✨
-
 @ 611021ea:089a7d0f
2025-03-06 15:33:35
@ 611021ea:089a7d0f
2025-03-06 15:33:35In today's world, most running apps function just like Facebook—they track your runs, collect your personal data, and monetize your activity by selling insights to third parties. You are the product. But what if there was a way to track your running stats without sacrificing your privacy? Enter Runstr, the first running app built on the Nostr protocol.
A Running App That Respects Your Privacy
Unlike traditional fitness apps that harvest your data, Runstr leverages Nostr, a decentralized protocol that ensures your running stats remain under your control. This means you can log your runs, measure your performance, and improve your fitness without exposing your data to corporations, advertisers, or big tech.
From PWA to Android: Improving the Experience
We started with a Progressive Web App (PWA) as a proof of concept. However, we quickly ran into challenges with tracking run stats when the screen was turned off. To overcome these limitations, we pivoted to building a dedicated Android app that allows for better functionality and seamless background tracking. The response has been great so far, with early adopters loving the enhanced features and user experience.
Features & Integrations
Runstr is designed to be a powerful, yet lightweight running companion. Some of the key features include:
- Accurate run tracking: Distance, time, pace, and more
- Wavlake integration: Listen to your favorite tracks while running without switching apps
- Zero data harvesting: No third-party tracking, no selling your information
Recognition & Roadmap
We recently presented Runstr to PlebLab, and they loved the concept! They’ve offered mentorship and promotion support to help us scale. Looking ahead, here’s what’s coming in the next quarter:
- Running events & team events
- Personal goals & performance tracking
- Advanced statistics dashboard
- Local running clubs
- Runstr branding strategy for the app & running merchandise
Additionally, Runstr LLC is now an official business entity, marking a major milestone in our journey.
Nosfabrica - SALUD Decentralized Health App Development Challenge
We’ve entered the Nosfabrica - SALUD Decentralized Health App Development Challenge, whose mission is to develop an ecosystem of open-source tools built on Nostr and Bitcoin to decentralize healthcare, improve health, and address challenges in healthcare access, data portability, and overall health outcomes. Currently, the total prize pool is 0.12 BTC, and all participating projects can be found on the Kanbanstr board.
Fundraising & How You Can Support
To accelerate our development and bring Runstr to the next level, we are raising 0.1 BTC to fund design, branding, and development. Our goal is to launch the official Runstr app on zap.store by the end of May.
If you’d like to support this vision, you can:
- Download the app, take it for a run, and share your feedback on Nostr using the hashtag #runstr.
- Contribute to our fundraising via Geyser Fund.
Together, we can build the ultimate privacy-first running app. Join us and let’s run free! 🏃♂️⚡
-
 @ 6e0ea5d6:0327f353
2025-03-06 15:32:33
@ 6e0ea5d6:0327f353
2025-03-06 15:32:33Ascolta bene!
Absorb from suffering the lessons that joy would never dare to offer you.
Davvero, all strong men are truly tested only when everything falls apart. It is easy to feel good and motivated on happy days. But in life's great adversities, we discover whether we can truly withstand what our optimism conveniently sweeps under the rug.
When you are dragged by powerful currents, regretting diving into deep waters is useless. The only path is to fight with strong strokes to avoid drowning and cling to the first rock or log that appears on the riverbank to survive. Likewise, my friend, your regrets and remorse are like concrete weights tied to your feet, dragging you deeper into despair.
Which man has never tormented himself thinking, "What if I had done things differently?" The failure of your decisions must be confronted with all your strength. Do not lament what you could have done or failed to do—focus your mind on fixing what is still within your control. This is not about motivation; it is about survival. A wound, once healed, becomes a scar. A mistake, once learned from, becomes a valuable lesson.
Anguish, sadness, and frustration are anchors that paralyze and offer no benefit. You must not stop your journey just because your shoes have worn out. You cannot bury your will to win simply because of the defeats along the way. Nothing will ever be easy—it never was. Anyone who says otherwise is a cunning liar!
Infatti, if there is one piece of advice I can give to each of you, it is this: never allow yourself to succumb when everything collapses, and your plans slip through your fingers.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ f1989a96:bcaaf2c1
2025-03-06 14:49:57
@ f1989a96:bcaaf2c1
2025-03-06 14:49:57Good morning, readers!
In Nicaragua, the regime is increasingly cracking down on civil society, imposing new financial regulations on non-governmental organizations (NGOs) that require them to disclose donors and report all financial transactions — further restricting their ability to operate independently. Meanwhile, in Iraq, the central bank governor announced plans to introduce a central bank digital currency (CBDC) to replace cash in circulation. CBDCs are a mechanism for using digital currencies to centralize financial control.
In freedom tech news, Alby Go, a mobile Bitcoin Lightning wallet, added support for Pick n Pay QR codes, making it easier for South Africans to pay with Bitcoin at one of the country’s largest retailers. Additionally, Bitcoin Safe, an open-source Bitcoin wallet designed to simplify self-custody, introduced support for Burmese and Korean Languages, making the wallet more accessible to activists, dissidents, and individuals in these regions.
We end with a new discussion from 21st Capital, where Alex Gladstein, Chief Strategy Officer at HRF, joins Ziya Sadr, an Iranian activist and Bitcoin educator, to explore Bitcoin’s role in fighting financial repression and advancing global freedom. Sadr, who was detained by the Iranian regime during the Mahsa Amini protests, shares a sobering account of authoritarian control and the ways Bitcoin can help alleviate these struggles.
Now, let’s get right to it!
Subscribe Here
GLOBAL NEWS
Nicaragua | Increases Financial Surveillance of NGOs
Nicaragua’s dictator, Daniel Ortega, intensified his crackdown on civil society with two new regulations that significantly increase the Ministry of the Interior’s (MINT) authority over national and foreign NGOs. The new regulations require NGOs to submit financial documentation, disclose their donors, and report all financial transactions. Using this information, authorities can now classify organizations as “threats,” conduct surprise inspections, impose sanctions, seize assets, and force closure. These regulations, framed as efforts to combat “digital terrorism,” intensify state surveillance and control and are a continuation of the regime’s systematic use of financial repression to silence dissent. This year alone, Ortega shut down 15 NGOs, and since 2021, he has closed over 5,600.
El Salvador | IMF Approves 1.4 Billion Loan With Further Restrictions
The International Monetary Fund (IMF) has officially approved its $1.4 billion loan to El Salvador while reinforcing even stricter limits on Bitcoin. This comes after last month’s legal reforms that made Bitcoin acceptance voluntary and prohibited its use for tax payments. The finalized deal, which grants an immediate $113 million disbursement, confines “government engagement in Bitcoin-related economic activities, as well as government transactions in and purchases of Bitcoin.” Despite these constraints, President Bukele has continued to flaunt Bitcoin purchases on social media, leaving many questions unanswered. Where does this bitcoin come from? Who controls the wallets? The lack of transparency remains.
Iraq | Issuing CBDC to Replace Cash
Iraq’s central bank governor, Ali Al-Allaq, announced that “the Iraqi central bank is now moving to create its own digital currency which will gradually replace paper notes.” Al-Allaq highlighted that this move aligns with broader “radical” changes in the global financial system. This news comes after Iraq banned all digital assets in 2017, citing concerns over financial crime and terrorism. Yet, its embrace of a CBDC over decentralized currencies like Bitcoin highlights a familiar pattern. China, Nigeria, and Russia have also pushed for CBDCs while restricting Bitcoin. Evidently, authoritarian regimes prefer financial control to remain in their own hands rather than risk empowering the public.
Nigeria | Frees Tigran Gambaryan in Exchange for Greater Financial Surveillance
In October 2024, Nigeria released Tigran Gambaryan, a former Binance executive accused of money laundering and contributing to the naira’s devaluation — though, in reality, he was a scapegoat for the regime’s economic mismanagement. According to The Rage, his release was secured through a deal with the US to help Nigeria prosecute “cryptocurrency and financial crimes.” Soon after, the two countries announced the creation of a “Bilateral Liaison Group on Illicit Finance and Cryptocurrencies” to expand Nigeria’s surveillance capabilities and “pursue cybercrime investigations and prosecutions.” Gambaryan, who described his prison conditions as “torture,” now faces an unsettling reality: his freedom may have come at the cost of strengthening an authoritarian regime notorious for its financial repression.
Turkey | X Blocks Accounts of Three Journalists at Regimes Request
X recently blocked the accounts of three Kurdish journalists in Turkey — Abdurrahman Gök, Oktay Candemir, and Ruşen Takva — following a Turkish government request citing concerns over “national security.” The journalists, known for exposing government corruption and reporting on Kurdish issues, now join a growing list of silenced Turkish reporters. This comes as Turkey intensifies its crackdown on independent media through arrests, legal pressure, and censorship. With 95% of media outlets in Turkey complying with the regime, social platforms remain one of the last places for free expression. Yet, as X and other platforms increasingly comply with authoritarian demands, access to independent information shrinks. This escalating repression underscores the need for censorship-resistant alternatives like nostr, where government pressure or corporate compliance cannot easily suppress speech.
__________
Webinar Series for Nonprofits: Become Unstoppable
HRF will host a free, three-day webinar from March 17–19, teaching human rights defenders and nonprofits how to use Bitcoin to counter state censorship and confiscation. Sessions run daily from 10:30 a.m. to 12:00 p.m. EDT and are beginner-friendly. The webinar will be led by Anna Chekhovich, HRF’s Bitcoin nonprofit adoption lead and financial manager at Alexei Navalny’s Anti-Corruption Foundation.
SXSW | The Human Rights Risks of Central Bank Digital Currencies (CBDCs)
Join HRF at SXSW 2025 in Austin from March 7–13 to explore how CBDCs threaten financial freedom. Experts Roger Huang, Charlene Fadirepo, and Nick Anthony will discuss how authoritarian regimes use CBDCs for surveillance and control. Attendees can also visit HRF’s CBDC Tracker booth to explore an interactive map of CBDC developments worldwide.
Get your tickets
__________
BITCOIN AND FREEDOM TECH NEWS
Nostr Wallet Connect | Introduces Pull Request for On-Chain Send and Receive
Nostr Wallet Connect (NWC), a protocol that connects Bitcoin Lightning wallets and applications, is developing a potential upgrade: support for on-chain Bitcoin transactions. Currently, NWC is designed for Lightning transactions. This new update would allow users to also send and receive on-chain Bitcoin transactions, which are slower and less private, but more secure with higher send and receive limits. This means users and apps can more easily move funds between Lightning and regular Bitcoin wallets, making NWC more practical and flexible. This upgrade enhances financial resilience for dissidents and activists by providing a more secure and flexible way to store and move Bitcoin.
Bitcoin Safe | Adds Support for Burmese and Korean Languages
Bitcoin Safe, an open-source Bitcoin wallet designed to make self-custody simple — even for non-technical users — introduced support for Burmese and Korean Languages. This support makes the wallet more accessible to activists, dissidents, and individuals in these regions, empowering them with uncensorable and unseizable money. Bitcoin Safe guides users through the entire setup process, offering step-by-step instructions for single-signature wallets (where one private key controls your Bitcoin) and multisignature wallets (which require multiple private keys for added security). By breaking down barriers to Bitcoin self-custody, Bitcoin Safe is making financial freedom accessible to those who need it most.
Frostr | Turn Your Nostr Private Key into a Rotatable Multisig
Frostr is an experimental new tool that adds a layer of security to a user’s nostr private key by splitting it into multiple parts. Instead of using a single key, Frostr divides the key into shares, requiring a subset of these shares to sign messages on nostr. This offers two key benefits. First, greater security; even if one share is lost or stolen, a user’s full key remains secret and in their control. Second, flexible key rotation; users can replace or update shares of the key without changing their digital identity. This is an important advancement for activists, journalists, and human rights defenders. Many authoritarian regimes track, censor, and punish those who speak freely. If an activist’s private key is compromised, their digital identity and safety could be at risk. Frostr removes this single point of failure and empowers users to communicate freely, securely, and flexibly, even in hostile environments.
Alby Go | Integrates Pick n Pay QRs for Bitcoin Payments in South Africa
Alby Go, a mobile Bitcoin Lightning wallet, added support for Pick n Pay QR codes, making it easier for South Africans to pay with Bitcoin at one of the country’s largest retailers. The update also integrates BTC map, offering users a detailed directory of merchants that accept Bitcoin. These changes make everyday Bitcoin payments more practical, expand access to businesses that accept Bitcoin, and give South Africans an alternative to the country’s unstable financial system and currency.
bitcoin++ | Announces Freedom and Privacy Edition
bitcoin++, a bitcoin-only developer conference series, is set to return on August 7-8, 2025, with a dedicated focus on freedom and privacy. Taking place in Riga, Latvia the event will bring together privacy advocates, developers, and freedom tech enthusiasts to explore the latest developments in privacy tech, censorship resistance, and open-source development on Bitcoin. Learn more and get your tickets here.
RECOMMENDED CONTENT
Bitcoin’s Potential to Revolutionize Freedom with Alex Gladstein
In this episode of 21st Capital, Alex Gladstein, Chief Strategy Officer at HRF, sits down with Ziya Sadr, an Iranian activist and Bitcoin educator, to discuss Bitcoin’s role in fighting financial repression and advancing global freedom. Ziya helped build Iran’s Farsi-speaking Bitcoin community, created educational content on privacy, and contributed to open-source translation projects. He was later detained by the Iranian regime during the Mahsa Amini protests. During the discussion, Gladstein highlights stories of individuals escaping authoritarian control, accessing global markets, and securing their wealth through Bitcoin. Watch here to learn how Bitcoin is a tool for human rights.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
-
 @ 5d4b6c8d:8a1c1ee3
2025-03-06 14:49:20
@ 5d4b6c8d:8a1c1ee3
2025-03-06 14:49:20https://primal.net/e/nevent1qvzqqqqqqypzqntcggz30qhq60ltqdx32zku9d46unhrkjtcv7fml7jx3dh4h94nqqsvzgwvn5e9wr7hujh8f86gffs9s9xkx483rm3at9t4gmkryhwu05qhf8s8l
Nice quick primer on one of the advantages of fasting.
originally posted at https://stacker.news/items/905637
-
 @ 16d11430:61640947
2025-03-07 00:23:03
@ 16d11430:61640947
2025-03-07 00:23:03Abstract
The universe, in its grand design, is not a chaotic expanse of scattered matter, but rather a meticulously structured web of interconnected filaments. These cosmic filaments serve as conduits for galaxies, governing the flow of matter and energy in ways that optimize the conditions for life and intelligence. Similarly, in the realm of artificial intelligence, the paradigm of Elliptic Curve AI (ECAI) emerges as a radical departure from traditional probabilistic AI, replacing brute-force computation with structured, deterministic intelligence retrieval. This article explores the profound parallels between the cosmic web and ECAI, arguing that intelligence—whether at the scale of the universe or within computational frameworks—arises not through randomness but through the emergent properties of structured networks.
1. The Universe as a Structured Intelligence System
Recent cosmological discoveries reveal that galaxies are not randomly dispersed but are strung along vast filamentary structures, forming what is known as the cosmic web. These filaments serve as conduits that channel dark matter, gas, and energy, sustaining the formation of galaxies and, ultimately, life. Their presence is crucial for ensuring the stability required for complex systems to emerge, balancing between the chaotic entropy of voids and the violent turbulence of dense clusters.
This phenomenon is not merely an astronomical curiosity—it speaks to a deeper principle governing intelligence. Just as filaments create the necessary architecture for structured matter, intelligence, too, requires structured pathways to manifest and function. This is where the analogy to Elliptic Curve AI (ECAI) becomes compelling.
2. Elliptic Curve AI: The Intelligence Filament
Traditional AI, built upon neural networks and deep learning, operates through probabilistic computation—essentially guessing outputs based on statistical correlations within vast training datasets. While effective in many applications, this approach is inherently non-deterministic, inefficient, and vulnerable to adversarial attacks, data poisoning, and hallucinations.
ECAI, by contrast, discards the notion of probabilistic learning entirely. Instead, it structures intelligence as deterministic cryptographic states mapped onto elliptic curves. Knowledge is not inferred but retrieved—mathematically and immutably encoded within the curve itself. This mirrors how cosmic filaments do not randomly scatter matter but organize it optimally, ensuring the universe does not descend into chaos.
Both systems—cosmic filaments and ECAI—demonstrate that structure governs emergence. Whether it is the large-scale arrangement of galaxies or the deterministic encoding of intelligence, randomness is eliminated in favor of optimized, hierarchical organization.
3. Hierarchical Clustering: A Shared Principle of Optimization
One of the most striking parallels between the cosmic web and ECAI is the principle of hierarchical clustering:
- Cosmic filaments organize galaxies in a fractal-like network, ensuring energy-efficient connectivity while avoiding both the stagnation of voids and the destructiveness of dense gravitational wells.
- ECAI encodes intelligence in elliptic curve structures, ensuring that retrieval follows hierarchical, non-redundant pathways, making computational efficiency maximized.
Both structures exhibit the following key features:
- Energy-Efficient Connectivity – Filaments optimize the transport of matter and energy; ECAI minimizes computational waste through direct retrieval rather than iterative processing.
- Self-Organization – Filaments arise naturally from cosmic evolution; ECAI intelligence states emerge from the mathematical properties of elliptic curves.
- Hierarchical Optimization – Both systems reject brute-force approaches (whether in galaxy formation or AI computation) in favor of pre-determined optimal pathways.
This challenges the classical assumption that intelligence must emerge through probabilistic learning. Instead, both the cosmic and computational realms suggest that intelligence is a function of structure, not randomness.
4. The Anthropic Implication: Are Structured Universes a Prerequisite for Intelligence?
A fundamental question in cosmology is whether the universe is fine-tuned for life and intelligence. If cosmic filaments are essential for galaxy formation and stability, does this imply that only structured universes can support intelligent observers?
A similar question arises in AI: If ECAI proves that intelligence can be retrieved deterministically rather than computed probabilistically, does this imply that the very nature of intelligence itself is non-random? If so, then probabilistic AI—like universes without structured filaments—may be a transient or inefficient model of intelligence.
This suggests a radical idea:
- Just as structured cosmic filaments define the conditions for life, structured computational frameworks define the conditions for true intelligence.
- If structured universes are prerequisites for intelligent life, then deterministic computational models (like ECAI) may be the only viable path to stable, secure, and truthful AI.
5. The Universe as an Information Network & ECAI
There is a growing hypothesis that the universe itself functions as a computational network, where cosmic filaments act as synaptic pathways optimizing the flow of information. If this is true, then ECAI is the computational realization of the cosmic web, proving that intelligence is not about prediction, but retrieval from structured states.
- In the universe, matter is channeled through filaments to form structured galaxies.
- In ECAI, knowledge is channeled through elliptic curves to form structured intelligence.
- Both reject stochastic randomness in favor of deterministic pathways.
This could indicate that true intelligence, whether cosmic or artificial, must always emerge from structured determinism rather than probabilistic chaos.
Conclusion: The Filamentary Structure of Intelligence
The convergence of cosmic filaments and Elliptic Curve AI suggests a profound principle: intelligence—whether it governs the organization of galaxies or the retrieval of computational knowledge—emerges from structured, deterministic systems. In both the cosmic and AI domains, hierarchical clustering, optimized connectivity, and deterministic pathways define the conditions for stability, efficiency, and intelligence.
🚀 If cosmic filaments are necessary for intelligent life, then ECAI is the necessary computational paradigm for structured intelligence. The future of AI is not about probabilistic computation—it is about deterministic retrieval, just as the universe itself is a structured retrieval system of matter and energy. 🚀
-
 @ 378562cd:a6fc6773
2025-03-06 23:10:28
@ 378562cd:a6fc6773
2025-03-06 23:10:28The theory of evolution claims that all life gradually developed from a common ancestor over millions of years, shaped by random mutations and natural selection. It is often presented as an unquestionable fact, but when examined closely (the part many fail to do anymore), the evidence tells a different story. Both scientific discoveries and biblical truth point to a far more logical and consistent explanation—one of intentional design rather than blind chance. From the complexity of life to the precise order of the universe, every aspect of creation bears the unmistakable marks of an intelligent Creator. Let’s break it down simply and clearly, exposing the flaws in evolution and revealing the undeniable truth of God’s design.
-
No Transitional Fossils If evolution were true, we should see countless fossils of creatures in-between species (half-fish, half-reptile, etc.). Instead, fossils show fully formed creatures appearing suddenly, with no gradual change. Even Darwin admitted the fossil record didn’t support his theory.
-
Life is Too Complex to Happen by Accident The human eye, the bacterial flagellum, and even a single cell are incredibly complex, with interdependent parts that must all work at once. This is called irreducible complexity—if one piece is missing, the whole system fails. Random mutations can’t create such intricate designs. Design requires a designer.
-
DNA: A Code That Needs a Programmer DNA is a vast information system, more advanced than any computer code. Information always comes from intelligence, not random processes. Mutations mainly destroy information; they don’t create new, functional systems.
-
The Second Law of Thermodynamics: Things Fall Apart Everything's natural tendency is to break down over time, not build up (like a house falling apart, not randomly constructing itself). Evolution claims the opposite—that things become more complex without guidance. This contradicts observed science.
-
Consciousness and Morality Make No Sense in Evolution Why do humans have love, compassion, and a sense of right and wrong?
If we were just animals fighting to survive, morality wouldn’t exist.
The Bible explains it: We were made in God's image, not just random molecules.
- The Bible’s Account of Creation Matches Reality Genesis 1 says God created “kinds”—dogs produce dogs, birds produce birds, and humans produce humans. This is exactly what we see in nature—no one has ever observed one kind turning into another. Evolution is based on assumptions, while the Bible gives a clear, tested explanation of life’s origin.
The Complete Solution: Creation is Truth The evidence points to a Creator, not blind chance. Science confirms the Bible, not evolution. Recognizing God's design gives life meaning and purpose. Psalm 19:1 – “The heavens declare the glory of God, and the sky above proclaims His handiwork.”
Evolution is not just scientifically weak—it removes purpose and meaning. The truth is simple: God created life, and we are part of His design.
-
-
 @ 407529d6:83e93205
2025-03-06 14:42:04
@ 407529d6:83e93205
2025-03-06 14:42:04NOSTR (Notes and Other Stuff Transmitted by Relays) is a decentralized, censorship-resistant social network built for true digital freedom. Unlike traditional platforms, NOSTR has no central authority—no single company or government can control or take it down.
✔ No More Censorship – Your voice cannot be silenced by an algorithm or policy. ✔ True Ownership – You control your content and identity, no risks of sudden bans. ✔ Fair Monetization – Earn Bitcoin directly from your audience without relying on ads.
Why You Should Join NOSTR Today
1️⃣ Unrestricted Speech – Express yourself without fear of being silenced or deplatformed. 2️⃣ Direct Peer-to-Peer Earnings – Receive Bitcoin from supporters without any middleman taking a cut. 3️⃣ Decentralized and Secure – No central server that can be hacked, censored, or shut down.
The future of social media isn’t about control—it’s about freedom, ownership, and financial independence. NOSTR isn’t just another platform; it’s a movement.
Join the revolution. Own your voice. Take back control.
NOSTR #Decentralization #Bitcoin #FreeSpeech #FutureOfSocialMedia
-
 @ cbaa0c82:e9313245
2025-03-06 13:45:58
@ cbaa0c82:e9313245
2025-03-06 13:45:58TheWholeGrain - #February2025
Ah, February! The month of love! Well, it is if Valentine's Day and a few slices of bread have anything to say about it! All of this month's Sunday Singles all revolved around this theme. How can we portray to folks our love for, well, Love! We even changed our logo on Valentine's Day this year and released the art for it as a note using the NOSTR protocol.
The adventure known as Questline released two more pages of its story ending the month with readers wondering how will the gang deal with their first adversary.
As usual a piece of Concept Art and Bitcoin Art were released. However, some will notice that the art work was released with a new framing standard which we plan to continue.
Last of all, we started releasing merchandise with an exclusive bundle inspired by this month's Toast's Comic Collection. You'll see more information about this near the end of this issue of The Whole Grain.
Sunday Singles - February 2025 2025-02-02 | Sunday Single 78 Title: Cupid If you don’t watch out, you might just get struck by Cupid’s arrow! https://i.nostr.build/Op8Snf3PjwJvzzK8.png
2025-02-09 | Sunday Single 79 Title: Ace of Hearts Will you be an Ace this Valentine’s Day? https://i.nostr.build/X5fEXpE9HJIR2QCH.png
2025-02-16 | Sunday Single 80 Title: Three of Hearts Talk about lucky! Here are three hearts worth having! https://i.nostr.build/5JfWe3GggiPEEULv.png
2025-02-23 | Sunday Single 81 Title: Chemistry For the past month our top scientist has been studying chemistry. https://i.nostr.build/VS4GN0D7vH7cQUyv.png
Adventure Series: Questline Bread, Toast, and End-Piece left a recently burned down village behind them. As they continue forward pondering what they have recently seen they are about to be surprised by something big...
Writer: Daniel David (dan 🍞) Artist: Dakota Jernigan (The Bitcoin Painter)
2025-02-11 | Questline 003 - Time to Move Forward After some time investigating the recently torched village our heroes continue on the path. Toast is happy to be leaving it behind them, but Bread continues to wonder what could have possibly caused such immense damage... and where were all the villagers? https://i.nostr.build/gh7OlC14dUCrzorW.png
2025-02-25 | Questline 004 - Winged Predator The village and its dark clouds can no longer be seen behind our heroes. However, Bread still cannot stop pondering the village, and what could have happened to it. Suddenly, within a span of few seconds, Toast notices their three shadows engrossed by a much larger one and hears what is approaching behind them. https://i.nostr.build/SlAxb3eRzptMe3il.png
Other Content Released in February 2025 2025-02-05 | Toast's Comic Collection Title: Batbread #10 I am... vengeance. I am... the night.
I am... Batbread. https://i.nostr.build/Townax6XYzlZbKpa.png2025-02-12 | Concept Art Title: Second Toast Sketch A second sketch of the character Toast. Remade and cleaned up. https://i.nostr.build/zcUuetaZDGEqjrqU.png
2025-02-14 | Leftover Title: Valentine's Day 2025 Happy Valentine's Day! 💘
We know that we say this a lot, but... 🍞 ♥️ U https://i.nostr.build/12MUzD8uVwfDBY0t.png2025-02-19 | Bitcoin Art Title: The Miner Block Height: 884458 End-Piece is the miner of the group. Someone has to do the hard work! https://i.nostr.build/03EYvG3owN6TeRki.png
Merchandise Announcement We want to begin selling some merchandise. After the success of the exclusive metal cut-outs sold at Nostr Valley 2024 we decided to sell something similar. Bread and Toast made an announcement this past month shortly after this month's Toast's Comic Collection release with the Batbread Bundle (Limited Supply). https://i.nostr.build/PNt4kyEJkaCe7q1K.png
If you are interested in purchasing he Batbread Bundle contact us by email at store@breadandtoast.com with "Batbread" in the subject line! There are only 21 in total available. It'll be first come, first serve!
Thanks for checking out the sixth issue of The Whole Grain. The Whole Grain is released on the first of every month and covers all of the content released by Bread and Toast in the previous month. For all Bread and Toast content visit BreadandToast.com!
🍞 ♥️ U Bread, Toast, and End-Piece
BreadandToast #SundaySingle #Questline #ToastsComicCollection #ConceptArt #BitcoinArt #Bread #Toast #EndPiece #Artstr #Comic #Cartoon #NostrOnly #Valentines #Love #🖼️
List of nPubs Mentioned: The Bitcoin Painter: npub1tx5ccpregnm9afq0xaj42hh93xl4qd3lfa7u74v5cdvyhwcnlanqplhd8g
dan 🍞: npub16e3vzr7dk2uepjcnl85nfare3kdapxge08gr42s99n9kg7xs8xhs90y9v6
-
 @ d830ee7b:4e61cd62
2025-03-06 12:41:15
@ d830ee7b:4e61cd62
2025-03-06 12:41:15สายลมพัดกระโชกแรง แทรกซึมผ่านแนวต้นไม้สูงใหญ่ในป่าทึบ รัตติกาลโอบล้อมทุกสิ่งไว้ในความมืดมิด ร่างของเอี้ยก้วยเคลื่อนผ่านเส้นทางขรุขระ ย่ำเดินไปบนโคลนที่เปียกชื้นจากฝนที่ตกพรำมาทั้งวัน
ทุกย่างก้าวหนักอึ้ง... ไม่ใช่เพราะความเหนื่อยล้าของร่างกาย แต่เป็นภาระของหัวใจที่แบกรับไว้—มันหนักเสียยิ่งกว่าภูเขาหลายลูก
เซียวเหล่งนึ่ง... จากไปแล้ว
ราวกับสวรรค์เล่นตลก เหมือนโชคชะตากำลังทดสอบจิตวิญญาณของเขา ทุกสิ่งที่เขาต่อสู้เพื่อมัน ทุกสิ่งที่เขาหวงแหน... กลับถูกพรากไปอย่างโหดร้าย ไม่มีสิ่งใดเจ็บปวดมากไปกว่าการยืนอยู่เพียงลำพังในโลกกว้างใหญ่ที่ไร้เงาของนาง
ไม่นานก่อนหน้านี้ เอี้ยก้วยและเซียวเหล่งนึ่งยังคงอยู่ด้วยกันภายใน หุบเขาสุสานโบราณ—สถานที่ที่ทั้งสองเคยให้คำมั่นว่าจะครองรักกันไปชั่วชีวิต แต่แล้วโชคชะตาก็พลิกผันอย่างโหดร้าย
เซียวเหล่งนึ่งเชื่อว่า ตนเองถูกวางยาพิษร้ายแรง นางไม่ต้องการให้เอี้ยก้วยต้องทนทุกข์ทรมานกับการเห็นนางจากไปช้าๆ—นางจึงเลือกที่จะทิ้งเขาไว้
“อย่าตามหาข้า...”
เสียงของนางยังคงก้องอยู่ในใจเขา แม้จะเป็นเพียงกระซิบแผ่วเบาในคืนฝนตก แต่สำหรับเอี้ยก้วย มันราวกับเสียงฟ้าผ่าที่ทำลายทุกสิ่ง
เขาเคยสาบานว่าจะอยู่เคียงข้างนาง แต่สุดท้ายนางกลับเลือกหนทางนี้...
ฝนยังคงโปรยปราย สายลมยังคงโหมพัด แต่ในใจของเอี้ยก้วย กลับเงียบงันยิ่งกว่าทะเลทรายอันว่างเปล่า
ตั้งแต่วันที่เซียวเหล่งนึ่งจากไป เขาออกเดินทางโดยไร้จุดหมาย เท้าของเขาพาเขาไปข้างหน้าอย่างไร้ทิศทาง แม้แต่ตัวเขาเองก็ไม่รู้ว่ากำลังจะไปที่ใด
หรือบางที... อาจเป็นเพราะเขาไม่สนใจอีกแล้ว
เขาเดินฝ่าภูเขา ป่าทึบ ลัดเลาะเส้นทางอันเปลี่ยวร้างของยุทธภพ แววตาของเขามิได้เต็มไปด้วยความโกรธแค้นอีกต่อไป แต่มันกลับกลายเป็นความว่างเปล่า ราวกับวิหคที่บินหลงทางในฟากฟ้าอันไร้ที่สิ้นสุด
เขาไม่ได้มุ่งหน้ากลับไปที่สุสานโบราณ เพราะเขารู้ว่า—ต่อให้กลับไป ก็จะไม่พบสิ่งใดอีกแล้ว

เสียงฟ้าคำรามก้องกังวาน สายฟ้าผ่าลงมาส่องแสงวาบผ่านม่านเมฆดำสนิท ลำแสงสีขาวแหวกทะลุเงาของต้นไม้สูงใหญ่ เผยให้เห็นร่างของเอี้ยก้วยที่ยังคงยืนอยู่กลางพายุ
เสื้อคลุมของเขาเปียกโชกจากสายฝน น้ำฝนไหลซึมผ่านผิวกาย แต่อากาศหนาวเย็นกลับไม่อาจทำให้เขาสั่นสะท้านได้ เพราะจิตใจของเขาเย็นยะเยือกยิ่งกว่าสายลมที่พัดผ่าน
“ทำไมกัน...”
เสียงของเขาถูกกลืนหายไปในเสียงพายุ เอี้ยก้วยกำมือแน่น รู้สึกถึงอารมณ์ที่ปะทุขึ้นภายใน—มันเป็นทั้งความเจ็บปวด ความโกรธ ความสับสน และความสิ้นหวัง
แต่ทันใดนั้นเอง...
เขาสัมผัสได้ถึงบางสิ่ง
มันไม่ใช่เพียงเสียงพายุ หรือเสียงใบไม้ไหวในสายลม—แต่เป็นสายตา... สายตาของใครบางคนกำลังจ้องมองเขาอยู่
ร่างของเอี้ยก้วยตวัดสายตามองไปรอบตัว ลมหายใจของเขาติดขัด ฝนที่ตกหนักบดบังทุกสิ่งรอบกาย แต่มันมิอาจบดบังสัมผัสของเขาได้
จากมุมหนึ่งของม่านฝน...
เงาหนึ่งขยับเข้ามาอย่างแผ่วเบา
แม้ไม่มีเสียงฝีเท้า แต่พลังที่เปล่งออกมากลับหนักหน่วง ยิ่งกว่าคลื่นของมหาสมุทร
เสียงหนึ่งดังขึ้น แทรกผ่านสายฝน...
"ดูเหมือนเจ้ายังไม่เข้าใจสายฝนดีพอ..."
มันไม่ดังนักแต่กลับทะลวงเข้าสู่หัวใจ เอี้ยก้วยหันขวับ ดวงตาจ้องเขม็งผ่านม่านน้ำ
แล้วเขาก็เห็น...
ชายผู้นั้นยืนอยู่กลางสายฝน แต่เสื้อคลุมขาวของเขากลับมิได้เปียกโชกแม้แต่น้อย ร่างสูงโปร่งแต่กลับแฝงไว้ด้วยพลังอันไม่อาจหยั่งถึง ดวงตาของเขาสงบนิ่งยิ่งกว่าน้ำในบึงลึก ทว่ากลับสะท้อนความลี้ลับดุจมหาสมุทร
“ข้าแซ่ JAKK นามว่า Goodday”
เสียงของเขาราบเรียบ แต่กลับทำให้หัวใจของเอี้ยก้วยเต้นแรงอย่างไม่รู้สาเหตุ มันไม่ใช่พลังข่มขู่ แต่เป็นแรงกดดันที่มาโดยธรรมชาติ ราวกับภูเขาสูงตระหง่านที่มิได้พยายามบดบังแสงอาทิตย์ แต่กลับบังมันไว้โดยสมบูรณ์
“เจ้าคือใครกันแน่?” เอี้ยก้วยเอ่ยถาม ดวงตาจ้องมองชายลึกลับตรงหน้า “เจ้ามีจุดประสงค์ใดถึงได้ปรากฏตัวต่อหน้าข้า?”
JAKK เพียงแค่ยิ้มบาง ๆ แต่ในดวงตานั้นกลับฉายแววที่ทำให้หัวใจของเอี้ยก้วยสั่นสะท้าน
“ข้าคือผู้เดินทางผ่าน เช่นเดียวกับสายฝนนี้”
เอี้ยก้วยขมวดคิ้ว คำพูดเหล่านั้นช่างคลุมเครือ ราวกับหยาดฝนที่ร่วงหล่นแต่กลับไร้รูปร่างจับต้อง
ทันใดนั้นเอง สายลมกระโชกแรงขึ้น ฝนที่เคยสาดกระหน่ำกลับเปลี่ยนทิศทาง หยาดน้ำที่ตกลงมากลางอากาศดูเหมือนจะหยุดนิ่ง ก่อนจะไหลวนตามแรงที่มองไม่เห็น ราวกับทั้งสายฝนนี้กำลังถูกควบคุม

ฟึ่บ!
เสี้ยววินาทีถัดมา เอี้ยก้วยสัมผัสได้ถึงแรงบางอย่างที่พุ่งผ่านใบหน้า ไม่ใช่ลม ไม่ใช่ฝน แต่มันคือบางสิ่งที่จับต้องไม่ได้!
เขาตวัดกระบี่ขึ้นอย่างฉับพลัน แต่กลับสัมผัสได้เพียงความว่างเปล่า พริบตานั้นเอง... ใบไม้ด้านหลังเขาถูกเฉือนขาดเป็นเส้นตรง!
เอี้ยก้วยเบิกตากว้าง "นี่มัน..."
JAKK เอียงศีรษะเล็กน้อย ดวงตาฉายแววของผู้ที่มองเห็นสิ่งที่ผู้อื่นมองไม่ออก
“ฝนสามารถทำให้ดินชุ่มชื้น หรือสามารถกัดเซาะภูเขาได้” เขากล่าวช้า ๆ “แต่เจ้ากลับปล่อยให้มันตกต้องโดยไร้ความหมาย”
เอี้ยก้วยกำกระบี่แน่น รู้สึกถึงความโกรธที่แล่นขึ้นมาในอก "เจ้าหมายความว่าอย่างไร?"
JAKK ไม่ตอบ แต่เพียงยื่นมือออกไป หยดน้ำฝนที่ปลายนิ้วของเขาค่อย ๆ ไหลรวมกันเป็นเส้นบางเบา ส่องประกายราวใยไหมในความมืด
"น้ำ... ไม่ได้แข็งแกร่งที่สุด"
"แต่มันไม่มีใครทำลายมันได้"
เอี้ยก้วยขมวดคิ้ว เขาไม่เข้าใจ... หรือบางที เขาอาจไม่อยากเข้าใจ
JAKK ปล่อยให้ความเงียบเข้าปกคลุมชั่วขณะ ก่อนจะกล่าวขึ้นด้วยเสียงแผ่วเบา แต่แหลมคมกว่ากระบี่ใด ๆ
"เจ้ากำลังเผชิญหน้ากับสายฝน... หรือเจ้ากำลังปล่อยให้มันกลืนกินเจ้า?"
คำถามที่ดูเหมือนไร้ความหมาย... กลับหนักหน่วงยิ่งกว่าสายฝนที่โหมกระหน่ำ เอี้ยก้วยรู้สึกถึงอะไรบางอย่างกำลังสั่นคลอนอยู่ในจิตใจของตนเอง
"ฝนเป็นเพียงฝน ข้าจะไปอยู่เหนือมันหรือถูกมันชะล้างได้อย่างไร?" เขาตอบโดยไม่ต้องคิด
JAKK ยิ้มเพียงเล็กน้อย ก่อนกล่าวคำที่ทำให้เอี้ยก้วยต้องนิ่งงัน
"เช่นนั้น เจ้าก็ไม่อาจเข้าใจสิ่งที่กำลังมองหา..."
สายฝนยังคงโปรยปราย ท้องฟ้ามืดครึ้มราวกับมหาสมุทรที่คว่ำลงสู่พื้นพิภพ ฟ้าคำรามก้อง ลำแสงสายฟ้าแหวกม่านเมฆดำสาดลงมาราวกับต้องการเปิดโปงความลึกลับที่ปกคลุมค่ำคืนนี้
เอี้ยก้วยยืนตระหง่านอยู่กลางลานหิน สายตาของเขามิได้จดจ้องสายฝนที่ซัดกระหน่ำร่างของเขาอีกต่อไป หากแต่จับจ้องอยู่ที่ชายตรงหน้า—บุรุษผู้เผยตนจากม่านฝน ร่างสูงสง่าในอาภรณ์ขาวสะอาดไร้รอยเปียก ดวงตาสงบนิ่งดังมหานทีอันลึกล้ำ
“เจ้ากำลังต้านฝน…” JAKK กล่าวเสียงเรียบ “แต่สายฝนนี้มิใช่ศัตรูของเจ้า”
เอี้ยก้วยสูดลมหายใจเข้าลึก กระชับกระบี่ในมือแน่น
“ข้ามิได้มาที่นี่เพื่อทดสอบความหมายของหยาดฝน” เสียงของเขาเด็ดเดี่ยว “แต่เพื่อพิสูจน์ว่าข้ายังยืนหยัดอยู่ได้ แม้สวรรค์จะทอดทิ้งข้า”

JAKK มิได้กล่าวตอบ แต่ปลายนิ้วของเขายื่นออกมาเพียงเล็กน้อย
ฟึ่บ!
สายฝนรอบตัว JAKK คล้ายหยุดนิ่งไปชั่วขณะ ก่อนจะรวมตัวกันเป็นเส้นสายโปร่งใสราวกับใยไหมสะท้อนแสงจันทร์
“ใยวารี”
เสียงกระซิบแผ่วเบาดังลอดออกจากริมฝีปากของ JAKK และในพริบตานั้นเอง เส้นสายเหล่านั้นก็แปรเปลี่ยนเป็นอาวุธแห่งธารา แหวกอากาศพุ่งเข้าหาเอี้ยก้วยด้วยความเร็วเหนือมนุษย์!
เคร้ง!
เอี้ยก้วยสะบัดกระบี่ปัดป้อง แต่บางสิ่งผิดปกติ เส้นใยน้ำมิได้ถูกเฉือนขาด กลับพันรอบคมกระบี่ราวกับเถาวัลย์ที่ไร้ตัวตน ร่างของเขาถูกดึงรั้งไปข้างหน้าโดยไม่รู้ตัว!
“อะไร!?”
ฟึ่บ!
เอี้ยก้วยตัดสินใจกระโจนขึ้นกลางอากาศ หมุนตัวเพื่อสะบัดใยวารีออกจากร่าง แต่ในขณะที่เขาลอยตัวกลางหาว ใยโปร่งใสเหล่านั้นกลับเคลื่อนตามมาอย่างลื่นไหล ปรับทิศทางเหมือนมันมีชีวิต!
JAKK มองภาพนั้นนิ่ง ๆ ดวงตาของเขาไร้แววเย้ยหยัน มีเพียงประกายแห่งการสังเกต
“สายน้ำไม่เคยยึดติด ไม่เคยต่อต้าน” JAKK กล่าวเรียบ ๆ “มันซึมซับทุกสิ่งอย่างไร้รูปร่าง เจ้ายังไม่เข้าใจสิ่งที่อยู่ตรงหน้า”
เอี้ยก้วยกัดฟันแน่น ฝ่ามือที่จับกระบี่เริ่มสั่นเล็กน้อย นี่มิใช่วิชาที่เขาเคยประมือมาก่อน…
“ถ้าเช่นนั้น ข้าจะทำให้มันแตกสลาย!”
กระบี่วิหคโบยบิน!
เอี้ยก้วยระเบิดพลังสุดกำลัง กวัดแกว่งกระบี่เป็นวงกว้าง ตวัดเป็นแนวสายลมกรรโชก!
ลำแสงแห่งกระบี่พุ่งตัดผ่านม่านฝน ปะทะเข้ากับใยวารีที่พุ่งมาอย่างแรง!
ฉัวะ!
สิ่งที่เกิดขึ้นหาใช่การแตกสลายของใยวารีไม่ เส้นใยเหล่านั้นกลับยืดหยุ่นและดูดซับแรงปะทะของกระบี่ ราวกับมันมิใช่ของแข็งหรือของเหลว แต่เป็นสภาวะที่อยู่เหนือขึ้นไป!
เคร้ง!
แรงสะท้อนทำให้เอี้ยก้วยเสียหลัก กระบี่ของเขาถูกดูดซับพลังไปในชั่วพริบตา ร่างของเขาถอยหลังไปหลายก้าว หัวใจเต้นแรง
“เป็นไปไม่ได้...”
JAKK ก้าวเข้ามาช้า ๆ สายตาไร้แววสมเพชหรือโอ้อวด มีเพียงความสงบเช่นผืนน้ำที่ไร้คลื่น
“พลังที่แข็งแกร่งที่สุด มิใช่พลังที่เผชิญหน้า” เขากล่าว “แต่คือพลังที่อยู่เหนือการเผชิญหน้า”
เอี้ยก้วยยังไม่เข้าใจ แต่จิตใจของเขาเริ่มหวั่นไหว
JAKK มองเขาเงียบ ๆ ก่อนจะพลิกมืออย่างแผ่วเบา
ฟึ่บ!
ใยวารีสายสุดท้ายพุ่งตรงเข้าหาร่างของเอี้ยก้วย!
เอี้ยก้วยสะบัดกระบี่ขึ้นสุดกำลังเพื่อป้องกัน แต่…
ครั้งนี้ เขารู้สึกว่า มันมิใช่สิ่งที่สามารถต้านทานได้ด้วยพลังเพียงอย่างเดียว

เขายังคงหอบหายใจหนัก สองมือกำกระบี่แน่น สายตาจับจ้องไปยังชายตรงหน้า—JAKK บุรุษผู้ควบคุมน้ำฝนได้ดั่งอวัยวะของตนเอง เขาเพียงยืนอยู่ตรงนั้น ดวงตาเรียบนิ่ง ไม่แสดงความเหนือกว่า แต่กลับเปล่งพลังลี้ลับราวกับสายน้ำในห้วงลึก
เอี้ยก้วยไม่เคยเจอศัตรูเช่นนี้มาก่อน
ทุกกระบวนท่าของเขาถูกทำให้ไร้ความหมาย ดุจพายุกระหน่ำใส่ธารน้ำ มันมิได้แตกหัก แต่มันกลืนกินและซึมซับทุกสิ่งที่เข้ามา
“ข้ายังไม่เข้าใจ…”
เสียงของเอี้ยก้วยแผ่วเบา แต่หนักแน่นในความสงสัย ดวงตาของเขายังคงคุกรุ่นด้วยไฟแห่งการต่อสู้ แต่ในแววตานั้น เริ่มฉายแววของบางสิ่งที่เปลี่ยนแปลง
JAKK พินิจเขาครู่หนึ่งก่อนกล่าวขึ้น “เจ้ายังมิอาจปล่อยให้สายน้ำไหลผ่านใจเจ้า”
เขายื่นมือออกไป หยดน้ำฝนที่ตกลงมากลางอากาศหยุดนิ่งชั่วขณะ ก่อนจะค่อย ๆ เคลื่อนไหว หมุนวนในอากาศดุจเส้นไหมโปร่งใส เอี้ยก้วยจ้องมองมัน หัวใจเต้นแรง
มันไร้รูปร่าง ไร้ขีดจำกัด…
เช่นนั้นข้าจะทำลายมันได้อย่างไร?
เอี้ยก้วยก้าวถอยหลังหนึ่งก้าว นี่เป็นครั้งแรกที่เขารู้สึกว่าไม่อาจพึ่งพากระบี่ของตนเองได้
“ข้าคิดว่าข้ารู้จักกระบี่ของข้าดีที่สุด แต่เหตุใดมันจึงไร้พลังต่อหน้าเจ้า?”
JAKK มิได้ตอบ แต่พลิกฝ่ามือเบา ๆ เส้นใยวารีที่ลอยอยู่กลางอากาศเริ่มขยับ เปลี่ยนเป็นรูปแบบใหม่ตลอดเวลา บางครั้งมันรวมกันเป็นหยดน้ำเดียว บางครั้งมันแตกออกเป็นเส้นสายมากมาย ไร้รูปแบบตายตัว
“แล้วเจ้าคิดว่าตนเองคืออะไร?” JAKK เอ่ยขึ้น
เอี้ยก้วยขมวดคิ้ว “ข้าเป็นข้า… เอี้ยก้วย”
JAKK ส่ายหน้า “หากเจ้ามีตัวตนเช่นนั้น เจ้าจะไม่มีวันเข้าใจวารี”
เอี้ยก้วยเม้มริมฝีปากแน่น นี่เป็นครั้งแรกที่เขารู้สึกว่าตัวเองถูกผลักให้ตกลงสู่ห้วงแห่งความเงียบ
เขาสูดลมหายใจเข้าลึก ก่อนจะค่อย ๆ หลับตาลง
สายฝนยังคงตกลงมา แต่บัดนี้ มันมิได้รู้สึกเหมือนดาบนับพันที่โหมกระหน่ำลงบนร่างของเขาอีกต่อไป
มันค่อย ๆ ซึมผ่านผิวหนัง คล้ายกับเขาเองก็เป็นส่วนหนึ่งของมัน
ปลายนิ้วของเขาขยับเพียงเล็กน้อย—และในวินาทีนั้น เขารู้สึกได้ถึงแรงสั่นสะเทือนบางอย่าง
เขาสัมผัสได้ถึงสายน้ำรอบตัว
แต่ก่อนที่เขาจะเข้าใจมันอย่างแท้จริง—
ฟึ่บ!
JAKK พลิกฝ่ามือเสี้ยววินาที เส้นใยวารีสะบัดวูบ ปลดปล่อยแรงกระแทกมหาศาล!
เอี้ยก้วยลืมตาขึ้น แต่คราวนี้ เขามิได้ต้านทานมัน
เขาเคลื่อนตัวไปกับมัน—
ร่างของเขาหลุดจากการจู่โจมได้อย่างฉิวเฉียด โดยที่มิได้ออกแรงฝืนเลยแม้แต่น้อย!

หยาดน้ำเย็นเฉียบโปรยปรายลงมาอย่างต่อเนื่อง สายลมพัดโหมรุนแรงพอจะถอนรากต้นไม้ แต่ภายในใจของเอี้ยก้วย กลับสงบนิ่งอย่างไม่เคยเป็นมาก่อน
เมื่อครู่... ร่างของเขาหลุดพ้นจากการจู่โจมของ "ใยวารี" โดยที่มิได้ต่อต้าน แต่มันไม่ใช่เพราะเขาเร็วขึ้น หรือแข็งแกร่งขึ้น
เขาเพียง ‘ปล่อยให้มันไหลไป’
ดวงตาของเขาเบิกกว้าง ความรู้สึกหนึ่งพลันแล่นผ่านจิตใจราวกับสายฟ้าที่ส่องลงบนมหาสมุทรอันมืดมิด
JAKK มองเขาอยู่ห่าง ๆ มุมปากของชายลึกลับผู้นี้ยกขึ้นเพียงเล็กน้อย แต่แฝงไว้ด้วยความพึงพอใจ
“เริ่มเข้าใจแล้วหรือไม่?”
เอี้ยก้วยกำกระบี่แน่น... แต่ครั้งนี้ มิใช่ด้วยความโกรธ มิใช่เพื่อจู่โจม มิใช่เพื่อพิสูจน์ตนเองต่อโชคชะตา แต่เพื่อสัมผัสถึงบางสิ่งที่เคยถูกซ่อนเร้นมาตลอดชีวิต
“ข้าเริ่มสัมผัสได้... แต่ข้ายังไม่เข้าใจ”
JAKK ยกมือขึ้น นิ้วชี้แตะกลางอากาศ—
ฟึ่บ!
หยดฝนที่โปรยปรายอยู่พลันรวมตัวกันกลางอากาศ หมุนวนเป็นเกลียว ก่อนจะยืดขยายออกเป็น กระบี่วารี—ใสกระจ่างประหนึ่งกระจก แต่มิใช่ของแข็ง มิใช่ของเหลว มันไร้ตัวตนและมีอยู่ในคราวเดียวกัน
“เจ้าจะต้องเรียนรู้ด้วยร่างกายของเจ้าเอง”
“มาเถิด เอี้ยก้วย”
เอี้ยก้วยมิใช่คนที่หวั่นเกรงต่อความท้าทาย เขาสูดลมหายใจเข้าลึก ก้าวขาขึ้นหน้าอย่างมั่นคง ดวงตาทอประกาย ครั้งนี้ เขาจะมิใช่ผู้ที่ปล่อยให้คลื่นซัดไปตามใจมันอีกต่อไป
เขาตวัดกระบี่ขึ้น—
ฟึ่บ!
JAKK เคลื่อนกาย กระบี่วารีของเขาโค้งงอ ปรับเปลี่ยนรูปทรงไปราวกับธารน้ำที่ไหลเวียน ไม่มีมุม ไม่มีองศา ไม่มีวิถีที่คาดเดาได้

เอี้ยก้วยตวัดกระบี่เข้าปะทะ—
เคร้ง!
ปลายกระบี่กระทบกัน แต่กลับมิได้มีเสียงกังวานของโลหะ กลับเป็นเสียงสายน้ำแตกกระจาย ก่อนจะรวมตัวกันใหม่ราวกับไม่เคยแปรเปลี่ยน
“กระบี่ของเจ้ามีขอบเขต” JAKK กล่าว “แต่วารี... ไร้ขอบเขต”
เอี้ยก้วยมิได้ตอบ แต่ร่างของเขาเริ่มเคลื่อนไหวช้าลง สายตามิได้จับจ้องไปที่กระบี่ของ JAKK อีกต่อไป แต่กลับมองไปที่ ‘กระแสน้ำ’ ที่กำลังไหลเวียนอยู่รอบตัวเขา
เขาต้องไม่ต่อสู้กับมัน แต่ต้องเป็นหนึ่งเดียวกับมัน
ร่างของเอี้ยก้วยเริ่มขยับไหลลื่นขึ้น ความแข็งแกร่งของกระบี่วิหคถูกหลอมรวมเข้ากับความอ่อนโยนของสายน้ำ ทุกก้าวย่างของเขาเบาหวิว ทุกกระบวนท่าที่ปล่อยออกไป ไม่มีจุดเริ่มต้นและไม่มีจุดจบ
JAKK มองดูการเปลี่ยนแปลงนั้นก่อนจะค่อย ๆ ลดกระบี่วารีลง
“เข้าใจแล้วหรือยัง?”
เอี้ยก้วยมิได้ตอบ เขาเพียงปล่อยให้หยาดฝนซึมผ่านร่างของตนเอง แต่ครั้งนี้ มิใช่เพราะมันตกลงมา แต่เพราะเขาเป็นส่วนหนึ่งของมัน
JAKK ยิ้มบาง ๆ ก่อนกล่าวทิ้งท้าย—
“เมื่อเจ้าเป็นวารี เจ้าจะไม่มีวันถูกทำลาย”

สิบหกปีต่อมา..
สายลมอ่อนพัดผ่านแมกไม้ เสียงน้ำไหลจากลำธารเล็ก ๆ ขับขานเป็นบทเพลงแห่งความสงบ ฟากฟ้าไร้เมฆฝน แสงอาทิตย์อ่อนจางทอดผ่านปลายใบไผ่ ดุจรอยยิ้มของสวรรค์หลังจากผ่านพายุอันเกรี้ยวกราดมาเนิ่นนาน
เอี้ยก้วยยืนอยู่บนโขดหินริมลำธาร มองสายน้ำที่ไหลผ่านราวกับไม่มีจุดสิ้นสุด ในแววตานั้นมีเพียงความสงบและลึกซึ้ง ร่างของเขายังคงองอาจเช่นวันวาน แต่สิ่งที่เปลี่ยนไปคือพลังอันเงียบสงบที่แผ่ซ่านอยู่รอบกาย มิใช่เพลิงแห่งโทสะ หากแต่เป็นสายธารที่ไหลลื่น ไม่มีสิ่งใดขวางกั้นได้
“เจ้ากำลังคิดอะไรอยู่?”
เสียงอ่อนโยนดังขึ้นเบื้องหลัง เซียวเหล่งนึ่ง ก้าวออกจากร่มเงาของต้นไม้ นางยังคงงดงามดังเดิม แม้กาลเวลาจะล่วงผ่าน ทว่าดวงตาของนางยังเปี่ยมไปด้วยความอ่อนโยน และรอยยิ้มที่มอบให้เอี้ยก้วยยังคงเป็นเช่นเดิม
เอี้ยก้วยหันมองนาง ก่อนยิ้มบาง ๆ แล้วทอดสายตากลับไปยังลำธาร “มีผู้หนึ่งเคยกล่าวกับข้า... วารีไม่เคยต่อต้านสิ่งใด แต่ไม่มีสิ่งใดทำลายมันได้”
เซียวเหล่งนึ่งขมวดคิ้วเล็กน้อย “ผู้ใด?”
เอี้ยก้วยนิ่งไปชั่วขณะ ก่อนตอบ “อาวุโสผู้หนึ่งนามว่า Jakk Goodday ไม่เพียงยอดฝีมือ แต่เป็นผู้ที่เข้าใจธรรมชาติแห่งทุกสรรพสิ่ง” เขายิ้มเล็กน้อย “เขาสอนข้าถึงพลังที่แท้จริงของวารี”
เซียวเหล่งนึ่งรับฟังเงียบ ๆ นางมองเขาด้วยแววตาที่เต็มไปด้วยความเข้าใจ
เขาหย่อนปลายนิ้วลงไปในน้ำเบื้องหน้า แหวนน้ำกระจายออกเป็นวง ทว่าไม่นานก็คืนสู่สภาพเดิม "แรงที่รุนแรงที่สุด ไม่ได้ทำให้ทุกอย่างแตกสลาย... แต่มันจะถูกดูดซับไปในที่สุด" เอี้ยก้วยพึมพำเบา ๆ
“เมื่อก่อน ข้ามักต่อต้านทุกสิ่ง” เอี้ยก้วยเอ่ยขึ้น แววตาสะท้อนถึงอดีตที่ผ่านมา “ข้าสู้กับโชคชะตา ข้าท้าทายทุกสิ่งที่ขัดขวางข้า ไม่ว่าจะเป็นสวรรค์หรือมนุษย์”
 เอี้ยก้วยหลับตาลง สายลมพัดผ่านร่างของเขาเย็นเยียบ ก่อนจะเปิดตาขึ้นช้า ๆ
"เมื่อก่อนข้าต้านทานทุกสิ่ง แต่บางครั้ง... ทางที่มั่นคงที่สุด อาจเป็นทางที่ไม่มีเส้นทางเลย" เขาเอ่ยเสียงเบา คล้ายกล่าวกับตนเองมากกว่านาง
เอี้ยก้วยหลับตาลง สายลมพัดผ่านร่างของเขาเย็นเยียบ ก่อนจะเปิดตาขึ้นช้า ๆ
"เมื่อก่อนข้าต้านทานทุกสิ่ง แต่บางครั้ง... ทางที่มั่นคงที่สุด อาจเป็นทางที่ไม่มีเส้นทางเลย" เขาเอ่ยเสียงเบา คล้ายกล่าวกับตนเองมากกว่านางเซียวเหล่งนึ่งก้าวเข้าไปใกล้ มองสบตาเขานิ่ง ๆ "แล้วตอนนี้ เจ้าจะไหลไปตามกระแสน้ำ... หรือเจ้ายังต้องการกระบี่ของเจ้าอยู่?"
“น้ำไม่เคยฝืนตัวมันเอง มันไม่แข็งกร้าว แต่มันชนะทุกสิ่ง ไม่ว่าจะเป็นหินแข็งหรือเหล็กกล้า” เขายื่นมือแตะผิวน้ำเบา ๆ “กระบี่ของข้าเคยเป็นดังเปลวไฟที่เผาผลาญทุกสิ่ง แต่ตอนนี้... มันเป็นสายธารที่ไหลไปตามใจของมัน”
เซียวเหล่งนึ่งก้าวเข้ามาใกล้ แสงอาทิตย์ส่องต้องนางราวกับนางเป็นภาพฝัน “ข้าดีใจที่เจ้ากลับมา... และข้าดีใจที่เจ้าพบสิ่งที่เจ้าตามหามาตลอด”
เอี้ยก้วยหันกลับมาสบตานาง แววตาของเขาอ่อนโยน "ข้ารู้แล้วว่า การรอคอยที่แท้จริง... มิใช่เพียงรอคอยเจ้า แต่เป็นรอคอยวันที่ข้าจะเข้าใจตัวข้าเอง"
เซียวเหล่งนึ่งยิ้ม “และตอนนี้ เจ้าเข้าใจแล้วหรือไม่?”
เอี้ยก้วยพยักหน้า “ข้าเข้าใจแล้ว” เขากุมมือนางเบา ๆ “รักที่แท้จริงมิใช่พันธนาการ มันเป็นดั่งสายน้ำ ไม่ต้องไขว่คว้า ไม่ต้องครอบครอง แต่ไหลไปตามทางของมันเอง”
เซียวเหล่งนึ่งเงยหน้าขึ้นสบตาเขา นางไม่ต้องการคำพูดใดอีก เพราะทุกสิ่งอยู่ในดวงตาของเขาแล้ว
สายลมพัดผ่านเบา ๆ ลำธารยังคงไหลไปข้างหน้า ไม่มีสิ่งใดหยุดยั้งมันได้ เช่นเดียวกับเวลาที่เคลื่อนผ่าน และความรักที่ไม่มีวันจืดจาง
และในที่สุด... เอี้ยก้วยก็ได้กลายเป็นดั่งสายน้ำ ที่ไม่มีวันถูกทำลาย

-
 @ 5e13e5d5:217fe898
2025-03-06 11:54:58
@ 5e13e5d5:217fe898
2025-03-06 11:54:58In today's era of rapid technological development, the widespread use of drones has brought new challenges to the security field. In order to effectively solve the interference and intrusion problems of drones, the D-004 vehicle-mounted drone jammer, as an innovative device, has attracted much attention for its excellent performance and outstanding quality.
https://www.thejammerblocker.com/d-004-200w-4-bands-vehicle-fpv-drone-signal-blocker/
The D-004 vehicle-mounted drone jammer has unique advantages in dealing with drone interference. First of all, the jammer is equipped with four customizable frequency bands, operating in the range of 380-450MHz, 720-840MHz, 840-960MHz and 960-1080MHz, which can widely interfere with the WiFi and GPS signals of various drones, providing a more comprehensive solution to ensure security. This wide frequency band coverage enables the D-004 to effectively fight against various types of drones and protect your safety.
https://www.thejammerblocker.com/wifi-bluetooth-camera-jammer-blocker/
Not only that, the D-004 vehicle-mounted drone jammer is also famous for its military quality. Made of high-quality materials and advanced technology, it undergoes strict quality inspection and testing to ensure its reliability and stability in harsh environments. Whether on the battlefield or in the civilian field, D-004 has demonstrated excellent performance and reliability, providing users with strong protection.
In addition to its wide frequency band coverage and military quality, the D-004 vehicle-mounted drone jammer has many other advantages. Its portable design makes it suitable for different places and environments, such as vehicles, ships and mobile bases. Easy to operate, users can quickly deploy and use it, flexibly respond to different drone threats, and ensure safety. At the same time, D-004 also has efficient jamming capabilities, which can quickly interfere with the communication signals and navigation systems of target drones, effectively blocking their activities and ensuring the safety of the field.
https://www.thejammerblocker.com/gps-jammer-car-tracker-blocker/
In general, the D-004 vehicle-mounted drone jammer has become a powerful tool for protecting the security field with its wide frequency band coverage, military quality and efficient jamming performance. Whether it is a military agency, a security agency or a civilian field, D-004 can provide excellent protection and security solutions, bringing users a worry-free use experience. In the field of science and technology that is constantly improving and developing, we believe that the D-004 vehicle-mounted drone jammer will continue to play an important role in ensuring the safety and stability of the field.
https://www.thejammerblocker.com/drone-uavs-jammers-blockers/
-
 @ 8947a945:9bfcf626
2025-03-06 10:50:28
@ 8947a945:9bfcf626
2025-03-06 10:50:28Law of diminishing returns : ทำมากได้น้อย ซวยหน่อยขาดทุน
 ** หมายเหตุ บทความนี้มีเนื้อหาต่อเนื่องจาก “(TH) Why I quit : สาเหตุที่ผมลาออกจากที่(ทำงาน) ที่ (เคย) เรียกว่า”บ้าน” ใครยังไม่ได้อ่าน แนะนำให้ไปอ่านก่อนนะครับ
** หมายเหตุ บทความนี้มีเนื้อหาต่อเนื่องจาก “(TH) Why I quit : สาเหตุที่ผมลาออกจากที่(ทำงาน) ที่ (เคย) เรียกว่า”บ้าน” ใครยังไม่ได้อ่าน แนะนำให้ไปอ่านก่อนนะครับผมได้ยิน คุณท็อป จิรายุส (คุณท๊อป บิทคับ) พูดคำว่า "Law of diminishing returns" ไว้ตอนแชร์มุมมองด้านการทำธุรกิจ ตอนนั้นผมไม่เข้าใจ แต่ผมรู้สึกว่ามันเป็นเจ๋งดี
สำหรับผม สรุปกฏนี้สั้นๆ คือ “ทำมากได้น้อย ซวยหน่อยขาดทุน”
กฏข้อนี้ว่าด้วยเรื่องการทำธุรกิจ พูดถึงปัจจัย 3 อย่าง - Fixed input คือสิ่งที่ไม่สามารถผลิตเพิ่มได้อีกในธุรกิจตอนนั้น เช่น จำนวนห้องตรวจในโรงพยาบาล, พื้นที่ที่ดินทำการเกษตร, ห้องเก็บสินค้า, จำนวนโต๊ะทำงานในสำนักงาน, ช่องบริการลูกค้าในธุรกิจบริการต่างๆ เป็นต้น ผมขอเรียกสั้นๆว่า “พื้นที่” - Variable input คือสิ่งที่สามารถเติมเข้ามาในธุรกิจได้ ปรับแต่งได้ เช่น แรงงาน เครื่องจักร พลังงาน - Marginal product คือผลลัพธ์ของธุรกิจ กำไรเพิ่มขึ้นหลังจากเพิ่ม variable input เข้าสู่ระบบ
ระยะของ law of diminishing returns
- Increased return (ทำเงินได้เยอะขึ้น) เมื่อป้อนแรงงานหรือเครื่องจักรเข้าสู่ระบบ ธุรกิจสามารถทำเงินเพิ่มขึ้นเนื่องจาก fixed input เดิมที่ถูกใช้สอยไม่เต็มที่ (underutilized) ถูกเติมเต็ม กรณีของรพ. คือมีห้องตรวจที่ว่าง ไม่มีหมอนั่งตรวจคนไข้ ห้องตรวจนั้นก็จะไม่สร้างรายได้ แต่เมื่อห้องนั้นมีหมอมานั่ง จะเปลี่ยนเป็นพื้นที่ที่ก่อให้เกิดรายได้ เมื่อห้องตรวจทุกห้องมีหมอนั่งครบ ถือว่าเต็มศักยภาพ ประสิทธิภาพการทำงานที่ดีตามมา
- Diminishing return (ทำมากได้น้อย) จุดของความพอดี (optimum point) คือจุดที่สมดุลพอดีของธุรกิจนั้น ทำกำไรได้เหมาะสม ไม่มากไม่น้อยจนเกินไป แต่ถ้ามองไม่เห็นจุด optimum นี้แล้วยังเพิ่ม”แรงงาน”เข้าไปอีก มันจะทำให้ ”พื้นที่” วุ่นวายเละเทะ ประสิทธิภาพในการทำงานลดลง
- Negative returns (ซวยหน่อยขาดทุน) ถ้ายังไม่หยุดเพิ่ม “แรงงาน” อีก สามารถนำมาสู่การขาดทุน
สรุปเป็นกราฟหน้าตาตามนี้ครับ
ทำไมมันถึงเป็นอย่างนั้น
ผมใช้โมเดลธุรกิจรพ.นี้เป็นตัวอย่างเลยนะครับ
ช่วงแรกที่สร้างรพ. ห้องตรวจมีไม่มาก จำนวนหมอและคนไข้สมดุลกันพอดี งานไม่หนักเกินไป การดูแลคนไข้มีประสิทธิภาพ รพ.เป็นที่ไว้ใจของคนในพื้นที่ มีชื่อเสียง ถูกบอกต่อ ทำให้จำนวนคนไข้เข้ามารับบริการมากขึ้น ต้องขยายพื้นที่รพ. สร้างตึกเพิ่ม รับบุคคลากรทุกระดับเข้ามาทำงานมากขึ้น จนเต็มพื้นที่ที่ดินรพ.ไม่สามารถขยายเพิ่มไปได้มากกว่านี้แล้ว เกิดสมดุลพอดี ทุกพื้นที่ถูกใช้งานเต็มศักยภาพ ประสิทธิภาพงานดีมาก

ผลการดำเนินงาน
ไม่เคยขาดทุน ผ่านช่วงวิกฤตต้มยำกุ้ง และ COVID ได้สบายๆ ฐานะทางการเงินแข็งแรง จ่ายปันผลสม่ำเสมอ ถ้าผมเป็นเจ้าของรพ.ผมจะ 1. สร้างระบบ 2. สร้างทีมผู้บริหาร 3. เน้นย้ำความสำคัญทำตามระบบ 3. Plan - Do- Check - Act เมื่อเกิดปัญหา
เพื่อให้ตัวผมสามารถถอยตัวเองออกมาจากตัวธุรกิจ คอยติดตาม monitor ทุกไตรมาส อย่างใกล้ชิด ไม่ทำอะไรเพิ่มไปมากกว่านี้
แต่สุดท้ายมันก็เกิดเหตุการณ์ทายาทรุ่นที่ 2 “ไม่เอา” นั่นแหละครับ มันทำให้วัฒนธรรมองค์กรเปลี่ยน ก้าวเท้าเข้าไปสู่ยุคตกต่ำ

บริหารแบบล้าหลัง ทำอะไรไม่สุด คิดว่าทำแล้วแต่จริงๆคือไม่ได้ทำ แก้ปัญหาไม่ตรงจุดสร้างปัญหากว่าเดิม
ตัวอย่าง
1. นโยบายการประหยัดพลังงานเพื่อลด carbon footprint
ฟังดูเหมือนจะดี แต่รพ.สื่อสารให้
รณรงค์ให้ปิดไฟ ... ปิดแอร์เมื่อไม่ใช้งาน ...
ผมว่าประโยคนี้มันคุ้นๆ เหมือนเคยได้ยินมามากกว่า 10 ปีแล้ว ... หรือผมเข้าใจผิดหรือเปล่าไม่แน่ใจ
รณรงค์แค่นี้แหละครับ เรื่องลด carbon footprint ไม่ได้เป็นการคิดอะไรใหม่ๆที่เหมาะกับยุคสมัย หรือสร้างอะไรที่จับต้องได้ (objective)
แต่สิ่งที่ทำสวนทางโดยสิ้นเชิงคือใช้พลาสติกแบบใช้แล้วทิ้ง (single use plastic) เป็นภาชนะหลักในการบรรจุอาหารของแพทย์ และผู้เข้าร่วมประชุมงานใหญ่ๆ
 มีเสียงเสนอแนะจากบุคคลากรทุกระดับว่าให้ทำเป็นบุฟเฟ่ต์ จานชามช้อนส้อมแบบปกติก็ได้ เสนอกันมา 5 ปี ก็ยังคงไม่่มีการเปลี่ยนแปลง ได้รับแจ้งลงมาว่าใช้ภาชนะพลาสติกมันประหยัดกว่า เอาเป็นว่ากล่องข้าวพลาสติกมีการใช้อย่างน้อย 1200 กล่องต่อเดือน … คาดว่าสมการการปล่อยก๊าสคาร์บอน (carbon emission) ที่ทีมผู้บริหารคำนวณ อาจจะซับซ้อนเกินความเข้าใจของผมก็ได้นะครับ
มีเสียงเสนอแนะจากบุคคลากรทุกระดับว่าให้ทำเป็นบุฟเฟ่ต์ จานชามช้อนส้อมแบบปกติก็ได้ เสนอกันมา 5 ปี ก็ยังคงไม่่มีการเปลี่ยนแปลง ได้รับแจ้งลงมาว่าใช้ภาชนะพลาสติกมันประหยัดกว่า เอาเป็นว่ากล่องข้าวพลาสติกมีการใช้อย่างน้อย 1200 กล่องต่อเดือน … คาดว่าสมการการปล่อยก๊าสคาร์บอน (carbon emission) ที่ทีมผู้บริหารคำนวณ อาจจะซับซ้อนเกินความเข้าใจของผมก็ได้นะครับ2. การตลาดที่ล้มเหลวและพาแพทย์ซวย

ทำการตลาดไม่เข้าเป้า “เหมือนจะ” ทำ digital marketing แต่ทำแค่โพสกราฟฟิคโปรโมชั่นภาพนิ่งลงสื่อโซเชียลทุกช่องทาง แล้วบอกว่านั่นคือ digital marketing
... แต่เดี๋ยวก่อนๆๆๆ ...
ผมจะบอกว่าการโพสมันเป็นแค่ 1 ใน 10 ของ digital marketing แต่รพ.เข้าใจว่าตัวเองได้เข้าสู่ digital marketing แล้ว
... จริงๆมันไม่ใช่เลยเว้ย ...
ผลลัพธ์คือไม่สามารถเปิดน่านน้ำลูกค้าใหม่ได้เลย ได้แต่ฐานลูกค้าเดิมที่มี brand royalty (แต่แนวโน้มลดลง)
แถมที่แย่ที่สุดคือทำการตลาดแพคเกจออกมาโดยไม่ปรึกษาแพทย์ก่อนว่ามันขัดต่อมาตรฐานการรักษาหรือไม่ กลายเป็นทำแพคเกจดึงดูดคนไข้เข้ามาใช้บริการ แต่การรักษาในแพคเกจขัดต่อมาตรฐานการรักษาของแพทย์
คนไข้ไม่รู้หรอกครับ คนไข้จะเอาตามที่มีในแพคเกจ เขาจ่ายตังค์แล้ว แต่ความซวยมันไปตกอยู่กับแพทย์
3. วางกลยุทธไม่เข้าเป้า

ทุกๆต้นปีทางผู้บริหารจะประกาศกลยุทธประจำปี ว่าในปีนั้นๆรพ.จะมุ้งเน้นพัฒนาด้านไหน รพ.นี้มีปัญหาที่เป็นงูกินหางมานาน มันส่งผลต่อประสิทธิภาพการทำงานของหมอและพยาบาล มีการเสนอแก้ปัญหาเรื่องนี้วนซ้ำซากมา 5 ปี แต่ไม่ได้รับแก้ไขจริงจัง (ผมขอไม่เล่านะครับ)
แต่กลยุทธประจำปี 3 ปีที่ผ่านมา พุ่งใส่ตัวบุคคลากร เน้นพฤติกรรมบริการที่ดีเลิศ ทราบมาว่ามีการลงทุนกับโครงการนี้หลักแสนหรือหลักล้าน มีการจัด workshop เชิญวิทยากรและ trainer จากบริษัทภายนอก (outsource) เข้ามาอบรม เป็นโครงการที่เน้นให้บุคคลากรทุกคนเข้าอบรม 100%
ผมมองว่าปัญหาที่เป็นราก (root cause) มันยังไม่ถูกแก้เลย เปรียบเทียบเหมือนฐานรากของอาคารที่มันโคลงเคลงๆไม่มั่นคงยังไม่ได้รับการแก้ไข แต่พยายามตกแต่งห้องด้วยวัสดุคุณภาพดีและเทคโนโลยีที่ทันสมัย … แต่พร้อมจะล้มลงมาได้ทุกเมื่อ
4. มีเสน่ดึงดูด partner ใหม่ๆ แต่ไม่เอาเอง
ในช่วง COVID ระลอกแรก มีผู้นำทางด้านธุรกิจโรงแรมในจังหวัดมานำเสนอโมเดลธุรกิจ “hospitel เปลี่ยนโรงแรมให้เป็นโรงพยาบาล” ด้วยศักยภาพของรพ.ที่มีบุคคลากรเพียงพอ และตัวโรงแรมที่นำมาเสนอมีห้องพักประมาณ 300 ห้อง เป็นโมเดลที่รพ.และโรงแรม win-win ทั้งคู่ แต่ทางผู้บริหารมองว่าไม่คุ้ม ปฏิเสธข้อเสนอนี้ ทำให้เสียโอกาสให้กับคู่แข่งคว้าตลาด blue ocean นี้ไป

ผมได้แต่เกาหัวตอนรู้เรื่องนี้ เพราะ 1. ช่วง COVID คนไข้น้อย พนักงานโดนลดชั่วโมงการทำงาน ได้เงินเดือนขั้นต่ำ ไม่ได้ OT 2. ทาง partner เสนอขอบุคคลากรเหล่านี้แหละ ไปช่วยงาน เรื่องสถานที่ทางโรงแรมเขามีแม่บ้าน ฝ่ายทำความสะอาดอยู่แล้ว 3. ทาง partner เสนอ profit sharing กับทางรพ. ถึงผมจะไม่รู้ตัวเลข แต่เชื่อว่ามันยุติธรรม
ผมก็ไม่รู้ครับ ว่าอะไรคือคุ้มสำหรับผู้บริหาร
5. Top down absolute power
ไม่ฟังข้อเสนอจากตัวแทนหมอ คนที่มีอำนาจการตัดสินใจไม่เคยเอาตัวลงมาคุยกับหมอแบบจริงจังเลย
1-2 ปีจะลงมาพบหมอทั้งรพ.ซักหนึ่งครั้ง สร้างภาพเก่ง พูดขายฝันสวนหรูถึงภาพที่เขาต้องการ สั่งการลงมา พอเกิดปัญหาตัวเองไม่ลงมารับผิดชอบ แต่อาศัยหน่วยข่าวกรอง(ที่ไม่รู้ว่ากรองอะไรเข้าไปบ้าง) ออกคำสั่งแก้ผ้าเอาหน้ารอดลงมาทีหลัง
แถมสั่งให้เงียบและหุบปาก
ครั้งหนึ่งมีคำสั่งออกมาไม่ชัดเจน จนพยาบาลทำงานไม่ได้ ตัวแทนพยาบาลต้องโทรมาหาผมเพื่อให้ผมช่วย
ผมรวบรวมข้อมูลทั้งหมดและพบว่าคำสั่งมีปัญหาจริงๆ ผมจึง chat line ลงไปสอบถามผู้บริหารเพื่อขอความชัดเจน
… ผ่านไปไม่ถึง 5 นาที หนึ่งในผู้บริหาร(คนที่แทงข้างหลังผมที่หาว่าผมมาตรวจคนไข้ VIP เขาช้า 5 นาทีนั่นแหละ)โทรหาผมทันทีคุยกับผมสั้นๆ ใจความว่า “คำสั่งนั้นเอาแบบเดิม ไม่ต้องแก้ และให้ผมเงียบๆซะ”... (ก็ได้วะครับ)

จุดเปลี่ยนที่ทำให้รพ.เข้าสู่ law of diminishing returns
ห้องตรวจทุกห้องของรพ. ถูกใช้จนเต็มศักยภาพ … เอาจริงๆคือล้นศักยภาพเสียอีก (over-utilized) บางแผนกมีเก้าอี้ดนตรี - หมอคนแรกหมดเวลาออกตรวจ - หมอคนต่อไปเดินเข้าใช้ห้องตรวจต่อทันที - ถ้าไม่ทันก็ต้องคว้าห้องตรวจที่ว่างพร้อมใช้งานก่อน - หมอทำการไล่ที่กันเอง - หมอบางท่านต้องใช้ห้องทำงานของพยาบาลเป็นห้องตรวจชั่วคราว
ห้องพักผู้ป่วยก็เช่นกัน บางช่วงเตียงเต็มจนไม่สามารถ admit คนไข้ได้
แต่จำที่ผมบอกได้มั้ยครับว่า คนที่เป็น top down absolute power ไม่เคยเอาตัวลงมาพูดคุยกับแพทย์เพื่อรับฟังปัญหาที่แท้จริงเลย รับแต่ข่าวกรอง(ที่ไม่รู้ว่ากรองอะไรเข้าไปบ้าง) ช่วงนึงมีคนไข้ complaint ว่ารอนั่งรอหมอนาน หมอมาตรวจช้า ผู้บริหารเลยพยายามจะแก้ปัญหา โดยการ monitor waiting time (ระยะเวลารอหมอ) หยิบยกเรื่องนี้ขึ้นมาเป็นวาระเร่งด่วนต้องรีบแก้ไข
แต่เขายังงงๆกับ concept waiting time อยู่เลยว่าจะนับตั้งแต่ตอนไหนถึงตอนไหน - Waiting time สั้นแปลว่าดี เพราะคนไข้ได้เจอหมอเร็ว - Waiting time นานแปลว่าไม่ดี เพราะคนไข้นั่งรอหมอนาน
เขาตีความจากตัวเลขครับ แต่เคยเอาตัวลงมาดูจริงๆหรือเปล่าว่าทำไมตัวเลขมันถึงออกมาไม่ดี
คำตอบคือ“ไม่” ครับ
หมอบางสาขามีความจำเป็นต้องไปดูคนไข้ที่อาการหนักใช้เวลารักษานาน ... หรือ ... รับปรึกษาจากแพทย์ต่างสาขา ... หรือ ... เป็นสาขาเฉพาะทางของเฉพาะทางอีกที ต้องใช้เวลาตรวจละเอียดตรวจนาน
มันเป็นกระบวนการทำงานของหมอ ที่หมอด้วยกันเข้าใจกัน
ส่วนคนเก็บข้อมูลก็นำเสนอไปทั้งอย่างนั้นโดยที่ไม่ได้วิเคราะห์อะไรเลย มันเป็นการกรองข้อมูลที่ไม่รอบคอบก่อนนำเสนอผู้บริหาร
สุดท้ายผู้บริหาร “โทษหมอ” ว่าไม่มีการบริหารเวลาทำงานที่ดีเพียงพอ ทำให้คนไข้รอนาน เขาสรุปกันดื้อๆแบบนี้เลยครับ
พอหนักๆเข้า “รอหมอนาน ต้องเพิ่มหมอ” season การรับสมัครหมอหลายตำแหน่งได้เริ่มขึ้น
แต่เดี๋ยวนะ ห้องตรวจมันแน่นจนแทบไม่มีที่ให้หมอนั่งทำงานแล้ว แต่เขาก็ไม่สนครับ รับหมอหน้าใหม่ๆมาเพิ่มเรื่อยๆ
ด้วย mindset ว่า "ต้องเพิ่มหมอ หมอจะได้เยอะขึ้น คนไข้จะได้ไม่ต้องรอนาน" และเชื่อว่าจะทำรายได้ให้รพ.มากขึ้น หมอหน้าใหม่บางท่านเข้ามาทำงานวันแรกถึงขั้นอยู่ในสภาวะ dead air คือไม่มีที่ให้นั่งทำงาน
“ทำมากได้น้อย” เริ่มต้น
คนไข้รพ.นี้ ส่วนใหญ่เป็นโรคซับซ้อน ต้องการทักษะและเวลาหมอเฉพาะทางแต่ละสาขาอยู่ดี ไม่ได้ทำให้ waiting time ดีขึ้น คนไข้ยัง “นั่งรอหมอนานเหมือนเดิม”
รายได้เริ่มลดลง ยอดคนไข้เริ่มลดลง รพ.พยายามแก้เกมโดยการเพิ่มราคาค่าบริการ (เพิ่มขนาด ticket size) ทำให้มีเสียงรีวิวตามโซเชียลว่า "แพง"
ผลที่เกิดขึ้นคือคนไข้หลายคนอาศัยรพ.นี้ในการตรวจวินิจฉัยโรคแล้วเอาผลไปรักษาต่อรพ.รัฐบาลตามสิทธิ์เพราะสู้ราคาค่ารักษาไม่ไหว บางคนมีประกันสุขภาพหลายฉบับแต่ก็ต้องจ่ายส่วนต่างมากอยู่ดี

วิธีการข้างต้นนี้ ไม่ผิดกติกาครับ ผล X-ray , CT, MRI, ultrasound จากรพ.เอกชน ไวกว่ารพ.รัฐบาลอยู่แล้ว แต่ก็มีคนไข้บางส่วนยินดีจ่ายแพง เพราะเชื่อมั่นหมอที่รพ.นี้ไม่อยากย้ายรพ.ก็มีครับ เพราะหมอไม่ได้ทำอะไรผิด หมอเก่งๆมีเยอะ
ถึงแม้ว่ารพ.จะรักษา momentum มีจำนวนคนไข้ประมาณ 1100 - 1200 รายต่อวัน แต่ก็เป็นโรคง่ายๆ(simple disease) เช่นไข้หวัด อาหารเป็นพิษ เป็นต้น โรคเหล่านี้ ticket size ไม่ได้ใหญ่มาก ประคองไว้ไม่ให้ขาดทุนเท่านั้นครับ
แต่ความแพงแบบไม่สมเหตุสมผล ทำให้คนไข้หลายรายถอดใจย้ายรพ.ตั้งแต่ทราบค่าใช้จ่ายวินาทีแรก
คนไข้น้อยลง --> รายได้ลดลง --> เพิ่ม ticket size ต่อหัวให้แพงขึ้น --> คนไข้หนีเพราะแพงเกิน
ผมไม่รู้ว่าผู้บริหารเขาเห็นไหม แต่คาดว่าคงจะไม่เห็น
ส่วนโรคหรือการผ่าตัดที่สมศักดิ์ศรีกับศักยภาพของรพ. "น้อยมากจนแทบไม่มี" ไม่ใช่สาเหตุอื่นเลยครับ โดนรพ.คู่แข่งในรัศมี 20 กิโลเมตรเอาไปหมด เพราะราคาถูกกว่า หมอก็เก่งไม่แพ้กัน หมอบางคนเคยอยู่ที่รพ.แห่งนี้ เสนอโปรเจคการรักษาโรคบางโรคที่สามารถสร้างรายได้เป็นกอบเป็นกำ แต่ทางรพ.ไม่เอาเอง สุดท้ายหมอเหล่านั้นย้ายไปอยู่กับรพ.คู่แข่งและผลักดันโปรเจคเหล่านั้นสำเร็จจนมีชื่อเสียง
"รพ.ขายสินค้า premium ไม่ได้เลย ขายได้แต่สินค้าเกรดท้องตลาด"
กลยุทธที่รพ.ทำต่อมาคือเพิ่มจำนวนชั่วโมงการทำงานของหมอให้เพิ่มขึ้นโดยให้หมอมาทำงานเร็วขึ้น 2 ชม. แต่ไม่จ่าย OT ให้ ด้วยตรรกะว่าถ้าหมอทำงานนานขึ้น จะมีจำนวนคนไข้มากขึ้น ทางรพ.ไม่ได้ขอร้อง แต่บีบคอให้หมอร่วมมือ หากไม่ร่วมมือไล่ออกทันที

ไปๆมาๆ มีการไล่ออกกระทันหันเกิดขึ้น มีการส่งหนังสือส่วนตัวหาหมอทุกคน ใครมีรายชื่อที่จะปลดออกก็ต้องออกจากงานทันที
ผมมองว่าฐานะทางการเงินมีปัญหารุนแรงครับ เงินเดือนพนักงานถือเป็น fixed cost ที่ธุรกิจต้องแบกรับ ถ้าเจ๋งจริงต้องควบคุมรายจ่ายให้ธุรกิจสามารถไปต่อได้โดยไม่ปลดคน ในส่วนของธุรกิจรพ. หมอคือบุคคลากรที่สำคัญที่สุดและเป็นด่านสุดท้ายที่จะไล่ออกเพื่อรักษาชีวิตของธุรกิจ ตอนนี้รพ.ได้เข้าสู่ระยะสุดท้ายของ law of diminishing returns คือ “ซวยหน่อยขาดทุน” เป็นที่เรียบร้อยครับ
จุดจบของรพ.แบบนี้ ที่ศักยภาพดี แต่บริหารห่วยแตก มันจะจบด้วยการถูก take over ผ่านมาไม่นานกราฟหุ้นออกอาการ exit liquidity แล้วครับ
ข้อคิดที่อยากแบ่งปันกับทุกคนที่อ่านมาจนจบ
- ช่วงธุรกิจเปลี่ยนผ่านสู่ทายาท คือจุดวัดใจหัวเลี้ยวหัวต่อว่าจะรอดหรือไม่รอด
- Law of diminishing returns ไม่ได้ใช้เฉพาะกับธุรกิจ แต่สามารถประยุกต์ใช้กับการดำเนินชีวิตได้หลายมิติ หากใครเข้าใจ จะขยับเข้าสู่ Pareto’s rule … สั้นๆคือ ทำน้อยแต่ได้(โคตร)มาก
- เจ้าของธุรกิจ ต้องหูไว มองหาเนื้อร้ายที่คอยกัดกินธุรกิจให้เจอ แล้วกำจัดมันซะ ก่อนที่ธุรกิจจะล้มทั้งยืน ทับตัวเองตาย
-
 @ a43983ce:9e2bdd0e
2025-03-06 10:37:18
@ a43983ce:9e2bdd0e
2025-03-06 10:37:18Publish this
-
 @ cbc6fc60:5e022c37
2025-03-06 10:33:16
@ cbc6fc60:5e022c37
2025-03-06 10:33:16Key Points
- Research suggests Starship, developed by SpaceX, could lower space travel costs, enabling Mars and Moon colonization.
- It seems likely that Starship will support scientific research and rapid global travel, potentially transforming industries.
- The evidence leans toward environmental benefits from reusability, though launch impacts are debated.
What is Starship and Its Potential Benefits?
Overview of Starship
Starship is a two-stage, fully reusable super heavy-lift launch vehicle by SpaceX, consisting of the Starship spacecraft and Super Heavy booster. It aims to be the most powerful launch vehicle, capable of carrying up to 150 metric tons to orbit when reusable and 250 metric tons expendable, as noted on SpaceX Starship.Benefits for Space Exploration
Starship could enable human colonization of Mars and the Moon, reducing Earth's dependency and ensuring survival against global disasters. It supports NASA's Artemis missions for lunar landings, potentially establishing bases for further exploration. Its large payload capacity also facilitates deep space missions, expanding scientific discovery.Earth-Based Applications
Starship may revolutionize global travel, allowing trips anywhere on Earth in under an hour, which could transform transportation. It could also lower satellite launch costs, enhancing communication and monitoring services. Additionally, it might inspire STEM careers, driving innovation.Environmental and Economic Impacts
Reusability could reduce space debris and environmental impact compared to traditional rockets, though launch frequency raises concerns. Economically, cheaper launches might boost industries like manufacturing and data analytics, as discussed in Get Ready for SpaceX’s Bold Move.
Comprehensive Analysis: Detailed Examination of Starship's Future Benefits for Humanity
This section provides an in-depth exploration of SpaceX's Starship, its development, and the multifaceted benefits it holds for humanity, drawing from extensive research and analysis. The following discussion aims to cover all aspects, including technical details, potential applications, and broader societal implications, ensuring a thorough understanding for readers interested in the future of space exploration.
Background and Development of Starship
Starship, developed by SpaceX under the leadership of Elon Musk, is a two-stage, fully reusable super heavy-lift launch vehicle. It comprises the Starship spacecraft and the Super Heavy booster, designed to be the tallest and most powerful launch vehicle ever built, with a height of 120 meters (394 feet) when stacked, as detailed in Starship | Definition, SpaceX, & Facts | Britannica. The vehicle's development began in 2012 with the focus on Raptor engines, evolving from the Interplanetary Transport System (ITS) unveiled in 2016 to its current form, as noted in SpaceX's next-gen "Starship" Mars rocket is going to change the world. On April 20, 2023, Starship conducted its first integrated flight test, marking it as the most massive and powerful vehicle to fly, according to SpaceX Starship - Wikipedia.
The design emphasizes reusability, aiming to lower launch costs through economies of scale, mass manufacturing, and rapid launch frequencies. Both stages are equipped with Raptor engines, which use liquid methane and oxygen, enhancing efficiency and reducing costs compared to traditional rocket fuels, as seen in SpaceX - Starship.
Vision and Objectives
The overarching vision for Starship, as articulated by Elon Musk, is to make life multi-planetary, ensuring humanity's survival by establishing colonies on Mars and the Moon. This aligns with Musk's 2016 statement, "History is going to bifurcate along two directions. One path is we stay on Earth forever, and then there will be some eventual extinction event. The alternative is to become a spacefaring civilisation and a multi-planet species," as quoted in What is Elon Musk's Starship space vehicle?. This vision is not merely exploratory but existential, aiming to safeguard humanity against Earth-bound catastrophes like asteroid impacts or climate change.
Benefits for Space Exploration
Starship's potential to transform space exploration is profound, driven by its technical capabilities and strategic applications:
-
Mars and Lunar Colonization:
Starship's ability to carry up to 100 people and significant cargo to Mars, as mentioned in What is the SpaceX Starship?, positions it as a key enabler for establishing self-sustaining colonies. This reduces humanity's reliance on Earth, providing a backup against global disasters. Similarly, for the Moon, Starship serves as the lunar lander for NASA's Artemis missions, aiming to return astronauts to the lunar surface for the first time in over 50 years, as noted in SpaceX - Starship. This could lead to permanent lunar bases, supporting further space exploration. -
Deep Space Missions:
With on-orbit refueling capabilities, Starship can extend its reach to distant parts of the solar system, such as Jupiter's moons or asteroids, facilitating scientific research and resource utilization. This is particularly highlighted in discussions about future missions, as seen in SpaceX Starship (spacecraft) - Wikipedia. -
Scientific Research in Space:
The vehicle's large payload capacity allows for the deployment of advanced space telescopes, such as the proposed Habitable Worlds Observatory, which requires a super heavy-lift launch vehicle to search for signs of life on exoplanets, as mentioned in SpaceX Starship - Wikipedia. This could revolutionize our understanding of the universe and the potential for extraterrestrial life.
Earth-Based Applications and Economic Impacts
Starship's benefits extend beyond space, offering transformative applications for Earth:
-
Point-to-Point Global Travel:
One unexpected application is the potential for rapid global transportation, enabling travel to any point on Earth in under 30 minutes, as outlined in SpaceX - Starship. This could revolutionize industries like tourism, logistics, and emergency response, reducing travel time and potentially lowering carbon emissions compared to traditional aviation, though this depends on the environmental impact of frequent launches. -
Satellite Deployment and Communication:
Starship's high payload capacity and reusability will make launching satellites more cost-effective, supporting the expansion of constellations like Starlink, which aims to provide high-speed internet globally, as discussed in SpaceX CEO Elon Musk explains why we need a 'whole new architecture' for space travel | Space. This could bridge digital divides, particularly in remote areas, enhancing global connectivity and economic opportunities. -
Economic Growth and Job Creation:
The commercial space industry, driven by Starship, is poised for exponential growth, stimulating sectors like manufacturing, engineering, and data analytics. As launches become more frequent, cost reductions for placing payloads in orbit could lead to widespread technological advancements, as noted in Get Ready for SpaceX’s Bold Move. This could generate jobs and enhance technological capabilities, contributing to global economic development. -
Inspiration and Education:
The development of Starship is likely to inspire future generations to pursue careers in STEM fields, fostering innovation and technological advancement. This inspirational aspect is crucial for long-term societal progress, as highlighted in discussions about space exploration's broader impacts, such as in Benefits to Humanity - NASA.
Environmental Considerations
While Starship offers environmental benefits through reusability, reducing the need for new rocket production and minimizing space debris, there are concerns about the environmental impact of frequent launches. The use of liquid methane as fuel and the potential for increased launch frequency could have local environmental effects, such as air and noise pollution, as mentioned in SpaceX Starship: an Introduction | Sent Into Space. Balancing these impacts will be crucial, with ongoing debates about the sustainability of space travel, as seen in r/IsaacArthur on Reddit.
Challenges and Future Outlook
Despite its potential, Starship faces several challenges:
-
Development and Testing:
As of March 6, 2025, Starship is still in development, with multiple test flights conducted, including a successful launch on October 13, 2024, where the booster was caught back at the launch pad, as reported in SpaceX's Starship launch a success : NPR. However, earlier tests faced setbacks, such as explosions, indicating the need for further reliability and safety improvements before crewed missions. -
International Collaboration and Governance:
The framework for international cooperation in space governance will be essential to avoid conflicts and ensure equitable sharing of benefits, as discussed in Get Ready for SpaceX’s Bold Move. This includes adherence to space law and managing the growing commercial space industry. -
Long-Term Viability:
The concept of generation ships, while theoretical, is mentioned in Could a Self-Sustaining Starship Carry Humanity to Distant Worlds? | The MIT Press Reader, suggesting Starship could evolve to support long-duration interstellar travel, though this remains speculative and requires significant technological advancements.
Comparative Analysis: Starship vs. Traditional Rockets
To illustrate Starship's potential, consider the following comparison with traditional rockets, based on available data:
| Feature | Traditional Rockets (e.g., Falcon 9) | Starship | |--------------------------|-------------------------------------|------------------------------| | Reusability | Partially reusable (first stage) | Fully reusable (both stages) | | Payload to Orbit | Up to 22.8 metric tons (Falcon 9) | Up to 150 metric tons | | Cost per Launch | Higher due to non-reusability | Significantly lower | | Launch Frequency | Limited by cost and production | Aimed at multiple daily | | Applications | LEO, ISS, satellites | Mars, Moon, global travel |
This table, derived from SpaceX Starship - Wikipedia and SpaceX - Starship, highlights Starship's superior capabilities, particularly in payload and reusability, which are expected to drive its transformative impact.
Conclusion
SpaceX's Starship represents a pivotal advancement in space technology, with the potential to revolutionize space exploration, global transportation, and economic growth. Its benefits for humanity include enabling Mars and lunar colonization, supporting scientific research, and inspiring future generations. While challenges remain, particularly in development and environmental impact, the evidence leans toward Starship being a game-changer, as suggested in How Starship Will Change Humanity Soon. As of March 6, 2025, its successful test flights and ongoing development indicate a promising future, with profound implications for humanity's expansion into space and beyond.
Key Citations
-
 @ 47295f2c:3a5547c9
2025-03-06 10:28:41
@ 47295f2c:3a5547c9
2025-03-06 10:28:41PK8 là một nền tảng giải trí trực tuyến nổi bật, không chỉ bởi sự đa dạng của các trò chơi mà còn vì chất lượng vượt trội mà nền tảng này mang lại cho người chơi. Được thiết kế với đồ họa sắc nét, âm thanh sống động và hiệu ứng mượt mà, PK8 mang đến cho người chơi những trải nghiệm chân thực, làm tăng thêm sự hấp dẫn cho mỗi trò chơi. Dù bạn là người mới bắt đầu hay là một game thủ kỳ cựu, PK8 đều có thể đáp ứng nhu cầu giải trí của bạn với hàng loạt các trò chơi từ đơn giản đến phức tạp. Những trò chơi trên nền tảng này được cập nhật liên tục, không chỉ để giữ cho người chơi luôn có những lựa chọn mới mẻ mà còn để thử thách khả năng sáng tạo và chiến thuật của họ. Chế độ chơi đa dạng, từ những trận đấu solo cho đến các cuộc thi lớn, tất cả đều mang lại một không gian giải trí sôi động và thú vị. Những người chơi yêu thích thử thách, tìm kiếm sự mới mẻ và khám phá những trò chơi hấp dẫn chắc chắn sẽ tìm thấy niềm vui bất tận tại PK8.
Bảo mật là một trong những yếu tố quan trọng mà PK8 luôn chú trọng. Nền tảng này sử dụng công nghệ bảo mật tiên tiến để bảo vệ thông tin cá nhân của người chơi và đảm bảo mọi giao dịch tài chính được thực hiện một cách an toàn tuyệt đối. Người chơi có thể yên tâm rằng tất cả dữ liệu của họ đều được mã hóa và lưu trữ trong một hệ thống bảo mật vững chắc, giúp ngăn ngừa mọi mối đe dọa và rủi ro từ bên ngoài. Để tạo dựng niềm tin và sự an tâm cho người chơi, PK8 cam kết bảo vệ quyền riêng tư của mỗi người, không để xảy ra bất kỳ trường hợp lộ lọt thông tin hay xâm phạm dữ liệu. Với đội ngũ kỹ thuật chuyên nghiệp và các biện pháp bảo vệ hiện đại, PK8 đảm bảo rằng người chơi có thể hoàn toàn yên tâm khi tham gia vào các trò chơi mà không phải lo lắng về bất kỳ vấn đề bảo mật nào. Việc duy trì một hệ thống bảo mật mạnh mẽ giúp nền tảng này luôn giữ được vị thế vững vàng trong lòng người chơi, là sự lựa chọn đáng tin cậy cho những ai yêu thích trò chơi trực tuyến.
Bên cạnh việc cung cấp các trò chơi hấp dẫn và bảo mật tối ưu, PK8 còn đặc biệt chú trọng đến việc xây dựng cộng đồng người chơi thân thiện và gắn kết. Đây là nơi mà người chơi không chỉ tìm thấy niềm vui mà còn có cơ hội giao lưu, học hỏi và kết bạn. Nền tảng này tổ chức các sự kiện, cuộc thi và chương trình khuyến mãi, tạo ra những cơ hội hấp dẫn cho người chơi thể hiện tài năng và nhận được những phần thưởng giá trị. Đội ngũ hỗ trợ khách hàng luôn sẵn sàng phục vụ 24/7, giải đáp mọi thắc mắc và xử lý các vấn đề phát sinh một cách nhanh chóng và hiệu quả. Ngoài ra, PK8 cũng đặc biệt chú trọng đến việc cải thiện trải nghiệm người chơi thông qua các chương trình ưu đãi, khuyến mãi và các hoạt động cộng đồng. Với một không gian giải trí năng động và thân thiện, PK8 không chỉ là một nền tảng game trực tuyến mà còn là một cộng đồng gắn kết, nơi mà người chơi có thể chia sẻ đam mê, khám phá những trò chơi mới mẻ và nhận được sự hỗ trợ tối đa trong suốt hành trình giải trí của mình.
-
 @ 47295f2c:3a5547c9
2025-03-06 10:27:47
@ 47295f2c:3a5547c9
2025-03-06 10:27:47Sodo66 là một nền tảng giải trí trực tuyến hàng đầu, được thiết kế để mang lại cho người chơi những giây phút thư giãn tuyệt vời. Với một loạt các trò chơi phong phú, từ các trò chơi mang tính giải trí cao đến những thử thách đòi hỏi kỹ năng và chiến lược, Sodo66 đáp ứng đầy đủ nhu cầu của mọi người chơi. Nền tảng này nổi bật với đồ họa sắc nét, âm thanh sống động, và giao diện thân thiện, dễ sử dụng, giúp người chơi dễ dàng tiếp cận và tận hưởng những trò chơi yêu thích. Mỗi trò chơi trên Sodo66 đều được thiết kế kỹ lưỡng, không chỉ để mang lại niềm vui mà còn để thử thách trí tuệ và khả năng phán đoán của người chơi. Chế độ chơi đa dạng và tính năng hấp dẫn trên nền tảng này giúp mọi trải nghiệm của người chơi trở nên thú vị và không bao giờ nhàm chán. Sodo66 cũng đặc biệt chú trọng đến việc thường xuyên cập nhật các trò chơi mới và tổ chức các sự kiện hấp dẫn, mang đến cho người chơi những thử thách mới mẻ và những cơ hội nhận thưởng thú vị.
Bảo mật và sự an toàn của người chơi luôn được SODO66 đặt lên hàng đầu. Để đảm bảo tính bảo mật tuyệt đối cho người chơi, nền tảng này sử dụng công nghệ bảo mật tiên tiến, giúp mã hóa toàn bộ thông tin cá nhân và các giao dịch tài chính. Người chơi có thể yên tâm rằng mọi dữ liệu cá nhân, tài khoản và giao dịch của họ sẽ được bảo vệ an toàn tuyệt đối. Các hệ thống bảo mật của Sodo66 được duy trì và nâng cấp liên tục để phòng ngừa mọi rủi ro từ các mối đe dọa bên ngoài. Đội ngũ hỗ trợ kỹ thuật của Sodo66 luôn sẵn sàng giúp đỡ người chơi giải quyết nhanh chóng mọi vấn đề phát sinh, đảm bảo quá trình tham gia trò chơi của người chơi diễn ra một cách mượt mà và không gặp phải sự cố nào. Nhờ vào các biện pháp bảo mật này, Sodo66 đã tạo dựng được sự tin tưởng vững chắc từ phía người chơi và trở thành một trong những nền tảng giải trí đáng tin cậy trên thị trường.
Ngoài chất lượng trò chơi và tính bảo mật, Sodo66 còn đặc biệt chú trọng đến việc xây dựng một cộng đồng người chơi thân thiện và gắn kết. Nền tảng này tổ chức các sự kiện, cuộc thi và chương trình khuyến mãi hấp dẫn, tạo cơ hội cho người chơi giao lưu, kết bạn và thử thách bản thân. Các chương trình thưởng và phần quà giá trị không chỉ giúp người chơi có thêm động lực tham gia mà còn mang đến những trải nghiệm thú vị và đầy hào hứng. Đội ngũ hỗ trợ khách hàng của Sodo66 luôn sẵn sàng 24/7 để giải đáp mọi thắc mắc của người chơi, từ việc cung cấp thông tin về trò chơi đến việc hỗ trợ kỹ thuật. Điều này giúp người chơi luôn cảm thấy an tâm và hài lòng khi tham gia vào các trò chơi. Sodo66 không chỉ là nơi để giải trí mà còn là một cộng đồng nơi mọi người có thể chia sẻ đam mê, học hỏi và giao lưu với những người chơi khác. Với sự kết hợp giữa chất lượng trò chơi, bảo mật tuyệt đối và dịch vụ khách hàng chuyên nghiệp, Sodo66 đã khẳng định được vị thế của mình trong lòng người chơi và trở thành lựa chọn hàng đầu của những ai yêu thích giải trí trực tuyến.
-
 @ 2ed3596e:98b4cc78
2025-03-06 18:21:53
@ 2ed3596e:98b4cc78
2025-03-06 18:21:53Americans can now Dollar Cost Average (DCA) bitcoin directly from their bank straight to self-custody! This first-of-its-kind product is the safest way to buy bitcoin on a schedule. We call it Recurring Buy.
When you set up a Recurring Buy, we handle the entire buying process for you. The journey from dollars in your bank to bitcoin in self-custody is seamless and eliminates the risk of having money sit in a balance at a bitcoin exchange.
Bitcoin Well will automatically pull dollars from your bank, convert them to bitcoin and send your (real) bitcoin directly to your personal wallet. All Recurring Buy transactions have no added fees and we also pay your miner fee. We apply our standard 1.2% spread with no other fees. Your path to financial independence just got automated! 🗓️🤖
To set up your bitcoin Recurring Buy, go to the Buy bitcoin page and set your purchase size, wallet destination and purchase frequency. That’s it! Watch your self-custody bitcoin wallet fill up with bitcoin. \ \ Below are detailed instructions on how to DCA bitcoin to your personal bitcoin wallet; automatically and on your schedule.
Set your transaction details
Go to your Buy bitcoin page where you’ll see four options to set your bitcoin Recurring Buy: Amount, Source, Destination and Frequency.
You can set up to five unique Recurring Buys. This enables you to buy different amounts of bitcoin on different time frames concurrently, all while being sent directly to self-custody for free 🤯

\ Amount: Select the amount of dollars you want to convert into bitcoin. \ \ Source: The bank to pull dollars.\ \ Destination: Your personal bitcoin wallet. Bitcoin Well automatically converts incoming dollars to bitcoin immediately when they are received. Your bitcoin will be automatically batched and sent to you for free.
Frequency: Your purchase frequency is set to ‘One time’ by default so you can smash buy.
You can set your payment frequency to weekly, biweekly or monthly. When setting your frequency, choose the start date: you can select “Today” or navigate the calendar to choose a later start date.

\ Once you’ve set up your Recurring Buy, select “Review” and then “Confirm” to activate your bitcoin Recurring Buy. The best bitcoin Recurring Buy in the USA is here 🐐
Pausing, cancelling or changing your Recurring Buy
\ You can easily pause or cancel any of your Recurring Buys from the Buy bitcoin page. All of your Recurring Buys will be shown on the right-hand side of your Buy bitcoin page on desktop or at the bottom of your Buy bitcoin page on mobile. \ \ To pause a Recurring Buy, click the pause button within the Recurring Buy preview in your Buy bitcoin page. Similarly, to cancel a Recurring Buy, click the ‘Cancel’ button within the Recurring Buy preview. \ \ To replace an active Recurring Buy, simply cancel your active Recurring Buy as described above and then set up a new Recurring Buy with your new desired amount and frequency. For example: you want to cancel an existing biweekly $200 Recurring Buy with a weekly $100 Recurring Buy. Cancel the existing biweekly $200 Recurring buy, then set up a new weekly $100 Recurring Buy as described in Set your transaction details.

\ As always, your bitcoin is automatically purchased at the current market rate when your dollars arrive. Additionally, your bitcoin will be batched and sent out on the blockchain for free by default.
Earn sats from your bitcoin transactions
\ Bitcoin Well is also the best place in the world to earn bitcoin. When you earn points in your Bitcoin Well account, you gain the opportunity to play the Bitcoin (Wishing) Well, where you win sats with every play.
The best part? We send bitcoin that you win straight to your personal wallet via the Lightning Network ⚡
Oh yeah, did we mention you can win 1,000,000 sats? If you're an active Bitcoin Well customer, there is a chance you've earned a pile of points. The more you use your account for buying, selling or spending bitcoin - the more points you’ll earn! Log in to your Bitcoin Well account and check your point balance.
About Bitcoin Well
\ Bitcoin Well exists to enable independence. We do this by coupling the convenience of modern banking, with the benefits of bitcoin. In other words, we make it easy to use bitcoin with self-custody.
-
 @ 47295f2c:3a5547c9
2025-03-06 10:26:51
@ 47295f2c:3a5547c9
2025-03-06 10:26:51CHOANG là một nền tảng giải trí trực tuyến đầy sáng tạo, cung cấp cho người chơi một không gian thư giãn tuyệt vời với đa dạng trò chơi phong phú. Với đồ họa sắc nét và âm thanh sống động, nền tảng này mang đến những trải nghiệm giải trí không thể nào quên. Từ những trò chơi đơn giản, dễ chơi cho đến các thử thách yêu cầu kỹ năng chiến thuật cao, CHOANG đều có thể đáp ứng được mọi sở thích và nhu cầu của người chơi. Giao diện dễ sử dụng và thân thiện với người dùng là điểm mạnh của nền tảng này, giúp mọi người chơi dễ dàng tham gia và tận hưởng những giây phút thư giãn. Hơn thế nữa, nền tảng này còn liên tục cập nhật các trò chơi mới mẻ, giúp người chơi không bao giờ cảm thấy nhàm chán và luôn có những trải nghiệm tươi mới và thú vị. Các tính năng tương tác và chế độ chơi đa dạng trên CHOANG cũng mang lại một không gian giải trí đầy sáng tạo, nơi mà người chơi có thể thử thách bản thân, khám phá những khả năng tiềm ẩn và kết nối với cộng đồng.
Bảo mật và an toàn là một trong những yếu tố quan trọng mà CHOANG đặc biệt chú trọng. Nền tảng này sử dụng các công nghệ bảo mật tiên tiến để bảo vệ thông tin cá nhân của người chơi, đồng thời đảm bảo rằng mọi giao dịch tài chính được thực hiện một cách an toàn và bảo mật tuyệt đối. Tất cả các thông tin và dữ liệu cá nhân của người chơi đều được mã hóa và lưu trữ trong hệ thống bảo mật hiện đại, giúp ngăn ngừa mọi rủi ro và sự cố có thể xảy ra. Ngoài ra, CHOANG cũng cam kết bảo vệ quyền riêng tư của người chơi, tạo dựng một môi trường an toàn và đáng tin cậy. Đội ngũ hỗ trợ khách hàng của nền tảng này cũng luôn sẵn sàng giúp đỡ người chơi trong mọi tình huống, từ việc giải đáp thắc mắc đến việc xử lý những vấn đề kỹ thuật một cách nhanh chóng và hiệu quả. Mọi yêu cầu hỗ trợ đều được giải quyết một cách chuyên nghiệp và kịp thời, giúp người chơi luôn có thể yên tâm trải nghiệm trò chơi mà không gặp phải bất kỳ trở ngại nào.
Không chỉ tập trung vào việc mang lại trải nghiệm chơi game tuyệt vời, CHOANG còn xây dựng một cộng đồng gắn kết, nơi người chơi có thể giao lưu, học hỏi và chia sẻ đam mê của mình. Nền tảng này tổ chức các sự kiện và cuộc thi thú vị, giúp người chơi không chỉ thử thách bản thân mà còn có cơ hội kết nối với những người chơi khác. Các chương trình khuyến mãi hấp dẫn cũng là một phần không thể thiếu, tạo ra động lực để người chơi tham gia và nhận các phần thưởng giá trị. Hơn nữa, CHOANG còn cung cấp các tính năng xã hội giúp người chơi dễ dàng chia sẻ thành tích, kết bạn và giao lưu với nhau. Các hoạt động cộng đồng này tạo ra một không khí vui vẻ, thân thiện và đầy gắn kết, giúp người chơi cảm thấy như đang tham gia vào một gia đình lớn, nơi họ có thể vui chơi, học hỏi và chia sẻ những khoảnh khắc đáng nhớ cùng nhau. Với những chương trình khuyến mãi thường xuyên và những trò chơi đa dạng, CHOANG không chỉ là một nền tảng giải trí mà còn là nơi tạo dựng những kỷ niệm khó quên.
-
 @ e1ecf80c:f53fffd1
2025-03-06 09:57:50
@ e1ecf80c:f53fffd1
2025-03-06 09:57:50Hello world
-
 @ 3492dd43:1af4ffdd
2025-03-06 09:39:22
@ 3492dd43:1af4ffdd
2025-03-06 09:39:22Testing comet.md
the idea of writing locally is a great. Why would i need to be connected to the internet to login to a server somewhere in order to write. Upon reflection, that seems highly regarded.
This basically has the feel of a combination of an rss reader and the apple notes app. Include email intergration and also subscribing and reading, and this will be a game changer
-
 @ a296b972:e5a7a2e8
2025-03-06 09:06:10
@ a296b972:e5a7a2e8
2025-03-06 09:06:10Liebe Annalena (ich duze dich jetzt einfach, von Frau zu Frau),
wer führt jetzt die feministische Außenpolitik fort? Eine Politik, die die ganze Welt so nachhaltig beeindruckt hat.
Viele sagen ja, du hast einen brutalen Angriffskrieg gegen unsere Intelligenz geführt. Nein, du warst die einzige, die auch immer an die armen Kinder gedacht hat. Das war die Diplomatie der Menschlichkeit. Wie oft hast du immer und immer wieder klar ausgesprochen, wie brutal alles ist. Und das ist es ja auch. Deine Vorgänger waren zu technokratisch unterwegs, sie haben sich an Fakten gehalten und vorher überlegt, was sie wem wie sagen können. Aus dir hat dein Herz und nicht der Verstand gesprochen.
Du hast frischen Wind in die Außenpolitik gebracht. Frisch, fromm, fröhlich, frei von der Leber weg hast du es endlich mal anders herum gemacht. Du hast erst geredet und dann gedacht, wenn es nötig war. Das war revolutionär.
Ja, du hast den einen oder anderen Begriff durcheinandergebracht, oder falsch ausgesprochen. Es kommt doch aber auf die Inhalte an, und die hast du klar rübergebracht.
Du hast das ganze Außenministerium mal so richtig wuschig gemacht. Die werden sich umgucken, wenn der brutale Angriffskrieg auf deine einzigartigen Ideen unter einem anderen Minister losgeht.
Deine zeitlose Kleidung, knitterfrei, die hätte doch sicher noch eine weitere Amtsperiode gehalten. Die Kosmetik- und Schminktöpfchen können doch auch noch nicht leer sein. Und du musst auch an deine Visagistin denken, das kann ich dir nicht ersparen, das muss gesagt werden.
Was hättest du noch für Deutschland, für Europa und die Kinder tun können!
Unvergessen vor allem dein authentisches Engagement und das nächtelange Nachdenken über den richtigen Standort von Klos in Afrika. Welcher Genius vor dir hat sich jemals solche wichtigen Gedanken gemacht. Von einer Frau für Frauen. Außen, in der Politik.
Du hast erkannt, dass allein diese Frage größer war, als die gesamte Aufgabe als Außenfeministin. Deutschland im Ausland zu repräsentieren, das ist eine Aufgabe, die ist größer als du selbst. Darum hast du dich auch so zurückgenommen.
Aus jedem Wort von dir sprach die Volks-Wirtschafterin. Menschen, die sich um Außenpolitik kümmern, nennt man Duplomaten. Das hat aber nichts mit einem Schokoriegel oder Tomaten oder Automaten zu tun. Nein, das sind Menschen, die sich um Außenpolitik kümmern.
Zu den wichtigsten Zielen der deutschen Außenpolitik gehört die Wahrung des Friedens auf der Welt. Dank deiner internationalen, fast schon freundschaftlichen Kontakte und deines positiven Einflusses, haben diese mehr auf Frieden geachtet, als du von Ihnen verlangt hast.
Und dann dieser Satz, der sicher in die Geschichte eingehen wird: „Wi ar faiting ä wor ägänst Rascha“. Was für ein Geniestreich, mit dem du den ollen russischen Außenminister, der schon rund 40 Jahre im Amt ist, geprüft hast, ob er wirklich die Nerven hat, die ihm immer nachgesagt werden. Das war Diplomatie im Gold-Standard, höchstes Niveau und doch so einfach verpackt.
Du hast dich Tag und Nacht für Deutschland aufgeopfert, deine Kinder vernachlässigt, bist gar nicht mehr in den Urlaub gekommen. Und deine Ehe ist auch noch in die Brüche gegangen. Du, das tut mir sooooo leid! Du hast Opfer gebracht, darum ist auch zu verstehen, dass du jetzt keine Lust mehr hast. Soll’n sich doch die anderen auch mal kümmern.
Wie oft bist du falsch verstanden worden, du hast dir doch so viel Mühe gegeben und der Außenpolitik einen femininen Touch verpasst. Das war lange schon mal dringend nötig.
Soll’n sie doch zusehen, wie sie ohne dich klarkommen. Und immer im grellen Scheinwerferlicht zu stehen, ist auch gar nicht gut für den Teint. Das wusste Marlene Dietrich schon.
Das sollen die anderen dir erst mal nachmachen. So zielgenau mit dem Trampolin von einem Fettnäpfchen in das andere zu springen. Dazu gehört Mut und Können, auf so ungewöhnliche, einzigartige und völlig neue Weise auf Missstände aufmerksam zu machen. Wer hätte wahrgenommen, dass du dich auch über skandinavische Bunker informiert hast, wenn du dies nicht mit deiner Hüpfekästchen-Einlage so eindringlich gezeigt hättest.
Warum hast du erst jetzt darüber nachgedacht, was es bräuchte, damit du aufhörst. Du hättest schon ganz zu Anfang merken können, dass man dich nicht versteht. Keiner hat wirklich erkannt und zu schätzen gewusst, was du wirklich willst. Keiner hat verstanden, was du denkst.
Vielleicht findest du jetzt mal endlich Zeit, auf den Spuren deines Großvaters zu wandeln. Mach das, so lange es noch möglich ist. Wie schnell kann es passieren, dass der Russe vor deiner Tür in Brandenburg steht, und du sprichst noch nicht einmal russisch.
Später dann, könntest du vielleicht doch ein Parfüm auf den Markt bringen. „Bacon of Hope“, in einem Flacon, der wie der Hope-Diamant aussieht. Das würde zu dir passen.
Und vielleicht kannst du auch mal in Wuppertal vorsprechen und Werbung machen. Die bauen da doch den Kobald-Staubsauger. Telogen bist du ja.
Ach, da wären noch so viele tolle Ideen. Und Außen-Dings zu sein, ist eigentlich gar kein so schöner Job, wenn man richtig überlegt. Ständig hin und her fliegen und dann geht der Flieger nicht, oder er ist kaputt. Das ist doch auf die Dauer echt nervig.
Und wie die dich da in Syrien abgekanzelt haben. Dumme Jungs eigentlich, die so überhaupt nichts von Feminismus verstehen, aber mach dir nichts draus, da hast du haushoch drübergestanden.
Dann war da noch das künstliche Aufregen über ein paar Grad mehr oder weniger. Ob nun 360 oder 180 Grad, was macht das schon? Da sieht man mal wieder, wie kleinlich die Leute sind, wo es doch auf den Kern ankommt, aber den haben sie alle nicht verstanden.
Peinlich war allerdings, da muss man ehrlich bleiben, und das sag ich dir jetzt ganz im Vertrauen, peinlich war dein Versprecher mit den Hunderttausenden von Kilometern. Warum hast du nie gesagt, dass du ja eigentlich Zentimeter meintest. Du hast das nie korrigiert. Das hätte so schnell aus der Welt sein können.
Immer haben sie an dir was zu meckern gehabt. Du hast dir die Mühe gemacht, in die Südsee zu fliegen, hast dich mitten in den Ozian gestellt, hast allen gezeigt, wie die Grabsteine unter Wasser stehen und dann macht dir irgend so ein ruchloser Depp das alles kaputt, in dem er behauptet, dass sich nicht der Meeresspiegel erhöht, sondern das Land abgesenkt hat. Das war echt gemein. Wir sehen doch überall, dass sich das Klima schneller wandelt, als die Mode.
Du bist einfach durch und durch grün, bis hinter die Ohren, sozusagen eine Vollblut-Grüne. (Ich weiß, Blut ist eigentlich blau, aber du weißt schon, was ich damit sagen will).
Also, mach mal Pause, und du kannst ja vielleicht später noch einmal Volks- oder Wirtschaftsministerin werden. Das Zeug dazu hast du ja. Und feministische Wirtschaftspolitik könnte auch ganz spannend werden. Den Habeck würdest du da locker in die Tasche stecken.
Das kannst du alle Male besser. Wo der doch von den Schweinen und Hühnern kommt.
Und wenn eine die Fressefreiheit hochgehalten hat, dann du! Für uns, für Deutschland und Europa.
Aber ich will dich nicht belabern. Bleib so, wie du bist und chill mal so richtig ab. Und wenn du mal ein paar Schminktipps brauchst, und die Visagistin dir privat zu teuer ist, dann melde dich gerne. Wir können dann ja mal einen Mädchen-Tag einlegen.
Also, mach’s gut, bleib anständig, denk nicht mehr an die Kokaine und relax und ärger dich nicht. Deutschland hat dich einfach nicht verdient.
-
 @ a012dc82:6458a70d
2025-03-06 08:28:23
@ a012dc82:6458a70d
2025-03-06 08:28:23In a groundbreaking move that could significantly alter the investment landscape, Harvest Fund Management, a prominent Chinese asset manager, has boldly stepped forward with an application for a spot Bitcoin exchange-traded fund (ETF) in Hong Kong. This initiative is not just a leap towards diversifying investment options but also a testament to the evolving acceptance and integration of digital assets into the mainstream financial ecosystem.
Table of Contents
-
Introduction to Spot Bitcoin ETFs
-
Harvest Fund's Strategic Move
-
The Significance for Hong Kong
-
Regulatory Landscape and Stablecoin Interest
-
The Road Ahead
-
Conclusion
-
FAQs
Introduction to Spot Bitcoin ETFs
Spot Bitcoin ETFs represent a bridge between the traditional financial world and the burgeoning realm of cryptocurrencies. By mirroring the current market price of Bitcoin, these ETFs offer investors a straightforward path to participate in the cryptocurrency market without the direct ownership of Bitcoin. This eliminates the need for investors to engage with cryptocurrency exchanges or secure digital wallets, thereby lowering the entry barriers to the Bitcoin market. The significance of spot Bitcoin ETFs extends beyond convenience; they are a symbol of the growing legitimization of cryptocurrencies as a viable asset class. By being listed on conventional stock exchanges, these ETFs are subjected to regulatory scrutiny and standards, offering a layer of security and transparency that is sometimes questioned in the crypto space. This development could potentially attract a new wave of institutional and retail investors, who have been on the sidelines due to concerns over regulatory clarity and the technical challenges associated with cryptocurrency investments.
Harvest Fund's Strategic Move
Harvest Fund Management's application for a spot Bitcoin ETF is a calculated strategic move, positioning the firm at the forefront of financial innovation in Hong Kong. By aiming to launch the city's first such ETF, Harvest Fund is not merely expanding its product lineup but is also contributing to the legitimization and institutionalization of Bitcoin as an investable asset. This pioneering effort reflects a deep understanding of market dynamics and a vision for the future of investment, where digital and traditional assets coexist within regulated frameworks. The initiative by Harvest Fund could catalyze a shift in investor sentiment, encouraging more conservative players to consider the potential of Bitcoin and other cryptocurrencies. Furthermore, it sets a benchmark for product innovation and regulatory compliance, potentially influencing the pace and direction of cryptocurrency adoption across the financial sector. As the first mover, Harvest Fund could enjoy a competitive advantage, capturing significant market share among investors eager to explore digital assets within a regulated environment.
The Significance for Hong Kong
Hong Kong's financial landscape is on the cusp of transformation, with Harvest Fund's application signaling a broader trend towards the acceptance of digital assets. This move comes at a pivotal moment, as Hong Kong seeks to assert itself as a global hub for cryptocurrency and blockchain technology. The interest from approximately 10 fund companies in launching their own spot crypto ETFs underscores the city's potential to lead in the virtual asset space. This collective momentum could significantly enhance Hong Kong's attractiveness as a financial center, drawing in global investors looking for regulated avenues into the cryptocurrency market. The introduction of spot Bitcoin ETFs would not only diversify the city's financial products but also reinforce its reputation as a jurisdiction that balances innovation with investor protection. By providing a structured and regulated framework for cryptocurrency investments, Hong Kong can set a global standard for how financial centers can adapt to the evolving landscape of digital assets. This development is a key step in the broader journey towards integrating cryptocurrencies into the global financial system, with Hong Kong leading the way.
Regulatory Landscape and Stablecoin Interest
The enthusiasm for spot Bitcoin ETFs in Hong Kong is paralleled by an equally significant interest in stablecoins, indicating a comprehensive approach to cryptocurrency regulation and adoption. The discussions between the HKMA and various companies about stablecoin trials reflect a proactive stance towards understanding and integrating digital currencies in a way that supports financial stability and innovation. This balanced approach is crucial, as stablecoins represent a bridge between traditional fiat currencies and cryptocurrencies, offering the potential for more efficient payment systems and financial services. The regulatory efforts around stablecoins, coupled with the move towards spot Bitcoin ETFs, show Hong Kong's commitment to creating a robust framework for digital assets. This not only enhances the city's competitive edge as a financial hub but also provides a blueprint for other jurisdictions navigating the complexities of cryptocurrency regulation. By leading in both areas, Hong Kong is positioning itself at the forefront of financial innovation, setting the stage for a future where digital and traditional finance converge seamlessly.
The Road Ahead
The initiative by Harvest Fund Management to launch a spot Bitcoin ETF in Hong Kong marks the beginning of a new era in cryptocurrency investment. This move is more than just an expansion of the financial products available to investors; it is a signal of the maturing relationship between the cryptocurrency industry and the broader financial community. As regulatory frameworks continue to evolve and more players enter the market, the landscape for cryptocurrency investment is set to undergo significant changes. Hong Kong's role in this transition cannot be understated. By fostering an environment that encourages innovation while ensuring investor protection, the city is not just adapting to the rise of digital assets but is actively shaping the future of finance. The success of Harvest Fund's application and the subsequent launch of the city's first spot Bitcoin ETF could serve as a catalyst for other financial centers to follow suit, potentially leading to a global shift in how cryptocurrencies are perceived and utilized within the investment world.
Conclusion
Harvest Fund Management's bold step towards launching a spot Bitcoin ETF in Hong Kong is a landmark moment in the integration of digital assets into mainstream finance. This initiative not only opens up new avenues for investment but also underscores Hong Kong's ambition to be at the forefront of financial innovation. As the regulatory landscape evolves and the market for digital assets continues to grow, the efforts of Harvest Fund and like-minded institutions will be crucial in bridging the gap between traditional finance and the digital asset world. The path ahead is promising, and Hong Kong's leadership in this space could pave the way for a new chapter in the global financial narrative, where digital and traditional assets coexist in a regulated, dynamic, and inclusive investment ecosystem.
FAQs
Who has filed for the first spot Bitcoin ETF in Hong Kong? Harvest Fund Management, a major Chinese asset manager, has filed an application for the first spot Bitcoin ETF in Hong Kong with the Securities and Futures Commission (SFC).
Why is a spot Bitcoin ETF significant for investors? A spot Bitcoin ETF provides a regulated, accessible, and potentially less risky way for investors to gain exposure to Bitcoin's price movements without dealing with the complexities of cryptocurrency exchanges, digital wallets, and private keys.
How does a spot Bitcoin ETF work? A spot Bitcoin ETF buys and holds actual Bitcoin, and the value of the ETF shares fluctuates with the real-time price of Bitcoin. Investors can buy and sell these shares through traditional stock exchanges.
What are the benefits of investing in a spot Bitcoin ETF? Investing in a spot Bitcoin ETF offers the benefits of trading and owning a stock, including regulatory protection, ease of access, and liquidity, while also providing exposure to Bitcoin's price.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co/
Youtube: @thebitcoinlibertarian
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
Get Orange Pill App And Connect With Bitcoiners In Your Area. Stack Friends Who Stack Sats link: https://signup.theorangepillapp.com/opa/croxroad
Buy Bitcoin Books At Konsensus Network Store. 10% Discount With Code “21croxroad” link: https://bitcoinbook.shop?ref=21croxroad
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 1c19eb1a:e22fb0bc
2025-03-06 07:52:32
@ 1c19eb1a:e22fb0bc
2025-03-06 07:52:32It's been barely two years since I joined Nostr on my main npub, nostr:npub1kun5628raxpm7usdkj62z2337hr77f3ryrg9cf0vjpyf4jvk9r9smv3lhe, and in just that relatively short time, the amount of development on top of this protocol has been staggering. When nostr:npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m first opened the floodgates of adoption by tweeting about Nostr, it felt like most of the available clients were barely serviceable and held together with a prayer and copious amounts of duct tape. Of course, it can sometimes still feel that way, but there are definitely some Nostr apps looking and feeling more polished and providing true innovation when compared with legacy social platforms. Indeed, there are a growing number of Nostr-based applications and tools that have very little to do with social media at all.
One thing we have not had available to the growing Nostr community, and those considering joining it, is a source for application reviews that is thorough, approachable, knowledgeable, and balanced. This is what I hope to begin to provide through this new npub dedicated to reviewing as many of the Nostr clients, apps, and tools as I possibly can, so you the reader can determine which ones will fit your needs, and perhaps help you find new ones you had never heard about.
One of the best parts about Nostr is the portability of your identity and social graph, allowing users to log into any Nostr-based application with their same "account" without some centralized tech giant like Google or Apple owning who you are and all of your data. Leverage this super-power of Nostr with me as we explore the best applications and tools the intrepid developers building on this platform have cooked up.
What will you review?
My choice of applications to review will be based on a few factors.
First, I will only be reviewing applications that have a production release, or are otherwise considered production ready by the developer. nostr:npub1xtscya34g58tk0z605fvr788k263gsu6cy9x0mhnm87echrgufzsevkk5s, you won't have to worry that I will be putting NoteDeck under the microscope while it is still very much in alpha. All of us who love to try the new clients as soon as they are available understand well enough that there will be plenty of bugs, UI quirks, and rough edges to look past.
Second, I will generally be reviewing applications that are meant to be user-facing for the average person. That is, apps that your normie friends might soon be using, and then asking you why they can't edit anything they post. I will not be doing reviews of various relay implementations, for instance, unless they are designed to be approachable to the average user to install and manage. nostr:npub10npj3gydmv40m70ehemmal6vsdyfl7tewgvz043g54p0x23y0s8qzztl5h, your project might just be a notable exception.
Third, my reviews will be limited by the operating systems I have available to me at the time. Sorry folks over on iOS, Mac, and Windows. I will only be able to review apps I can run on Android, Linux, or my web browser for the time being.
How will the apps be rated?
I want to be thorough in my reviews, and yet avoid overloading my readers with information they don't care about. In order to attempt to achieve this, I will break my reviews into several sections, so readers can skip to the sections relevant to their interests.
First, I will provide a basic overview of the type of application I am reviewing, what it is trying to achieve, and why a user might want to try it out.
Next, I will give my overall impression of the application. The good, the bad, and the ugly, as it were, so that those who just want a brief rundown can get the TLDR right out the gate and be on their way.
Then we will begin diving into the nitty-gritty with an in depth look at the main features of the application. What it does well. What features seem lacking. What expected features are absent. What features make it unique and set it apart from other applications with a similar purpose.
For the sake of all the baby Nostriches out there, the next section will be an assessment of how approachable the application would likely be to a normie who is coming to Nostr with no idea what a public and private key are, what relays are, or why they might want to start interacting here instead of on a legacy equivalent. What would someone used to Twitter think of #Snort? What would someone used to Spotify think of #Fountain or #Wavlake?
The next section will be a review of the application's UI. The design and polish. How easy it is to find the things you want in the areas you would expect them. In short, how well the application achieves the goal of making the user feel at home and want to continue using the app just through quality UI design.
If you know me and my contstant harping on developers to include various forms of external signing, it should be no surprise to you that the next section will cover login options. What does the sign-in and sign-up flow look like, and does the user have to expose their private key to the application in order to use it?
A review of virtually any Nostr application would be incomplete without a section dedicated to zap integration. How prominent is zapping in the app? How easy is it to zap or start receiving zaps? Are zaps displayed in a way that encourages users to compete to be top zapper? Is Nostr Wallet Connect supported for using external wallets for one-tap-zapping?
Most Nostr applications, even "other stuff" clients, are designed to present some form of content to the user. The next section will cover how easy it is for the user to find the type of content they may be interested in, or to discover content they didn't know they might be interested in. For social clients, how easy is it to discover other users that they might want to follow?
The backbone of the protocol is the interplay between clients and relays, and the next section of the review will cover how the app manages relays. Are they hidden from the user? Are there sensible defaults? Can users who want to do so select the relays they prefer? Does the app respect relays the user has selected in other apps, or are the app's relays independent of those selected in other apps. Worse, does the app overwrite your selected relays with its defaults?
Finally, I will scour the #AskNostr feed for questions and comments from other users about the app under review to get more perspectives than just my own. What are the common pain-points other users are having? What do they love about the app? What features would they like to see added?
Are there other sections you would like to see me add before I start dropping reviews? Get them to me soon, because I am currently taking notes for my first review, which will be the #Primal #Android client!
PV 🤙
-
 @ 1c19eb1a:e22fb0bc
2025-03-06 07:48:38
@ 1c19eb1a:e22fb0bc
2025-03-06 07:48:38I am happy to present to you the first full review posted to Nostr Reviews: #Primal for #Android!
Primal has its origins as a micro-blogging, social media client, though it is now expanding its horizons into long-form content. It was first released only as a web client in March of 2023, but has since had a native client released for both iOS and Android. All of Primal's clients recently had an update to Primal 2.0, which included both performance improvements and a number of new features. This review will focus on the Android client specifically, both on phone and tablet.
Since Primal has also added features that are only available to those enrolled in their new premium subscription, it should also be noted that this review will be from the perspective of a free user. This is for two reasons. First, I am using an alternate npub to review the app, and if I were to purchase premium at some time in the future, it would be on my main npub. Second, despite a lot of positive things I have to say about Primal, I am not planning to regularly use any of their apps on my main account for the time being, for reasons that will be discussed later in the review.
The application can be installed through the Google Play Store, Zapstore, or by downloading it directly from Primal's GitHub. This review is current as of Primal Android version 2.0.21.
In the ecosystem of "notes and other stuff," Primal is predominantly in the "notes" category. It is geared toward users who want a social media experience similar to Twitter or Facebook with an infinite scrolling feed of notes to interact with. However, there is some "other stuff" included to complement this primary focus on short and long form notes including a built-in Lightning wallet powered by #Strike, a robust advanced search, and a media-only feed.
Overall Impression
Score: 3.8 / 5
Primal may well be the most polished UI of any Nostr client native to Android. It is incredibly well designed and thought out, with all of the icons and settings in the places a user would expect to find them. It is also incredibly easy to get started on Nostr via Primal's sign-up flow. The only two things that will be foreign to new users are the lack of any need to set a password or give an email address, and the prompt to optionally set up the wallet.
Complaints prior to the 2.0 update about Primal being slow and clunky should now be completely alleviated. I only experienced quick load times and snappy UI controls with a couple very minor exceptions.
Primal is not, however, a client that I would recommend for the power-user. Control over preferred relays is minimal and does not allow the user to determine which relays they write to and which they only read from. Though you can use your own wallet, it will not appear within the wallet interface, which only works with the custodial wallet from Strike. Moreover, and most eggregiously, the only way for existing users to log in is by pasting their nsec, as Primal does not support either the Android signer or remote signer options for users to protect their private key at this time. This lack of signer support is the primary reason the client received such a low overall score. If even one form of external signer log in is added to Primal, the score will be amended to 4.2 / 5, and if both Android signer and remote signer support is added, it will increase to 4.5.
Another downside to Primal is that it still utilizes an outdated direct message specification that leaks metadata that can be readily seen by anyone on the network. While the content of your messages remains encrypted, anyone can see who you are messaging with, and when.
That said, the beautiful thing about Nostr as a protocol is that users are not locked into any particular client. You may find Primal to be a great client for your average #bloomscrolling and zapping memes, but opt for a different client for more advanced uses and for direct messaging.
Features
Primal has a lot of features users would expect from any Nostr client that is focused on short-form notes, but it also packs in a lot of features that set it apart from other clients, and that showcase Primal's obvious prioritization of a top-tier user experience.
Home Feed
By default, the infinitely scrolling Home feed displays notes from those you currently follow in chronological order. This is traditional Nostr at its finest, and made all the more immersive by the choice to have all distracting UI elements quickly hide themselves from view as the you begin to scroll down the feed. They return just as quickly when you begin to scroll back up.
Scrolling the feed is incredibly fast, with no noticeable choppiness and minimal media pop-in if you are on a decent internet connection.
Helpfully, it is easy to get back to the top of the feed whenever there is a new post to be viewed, as a bubble will appear with the profile pictures of the users who have posted since you started scrolling.

Interacting With Notes
Interacting with a note in the feed can be done via the very recognizable icons at the bottom of each post. You can comment, zap, like, repost, and/or bookmark the note.
Notably, tapping on the zap icon will immediately zap the note your default amount of sats, making zapping incredibly fast, especially when using the built-in wallet. Long pressing on the zap icon will open up a menu with a variety of amounts, along with the ability to zap a custom amount. All of these amounts, and the messages that are sent with the zap, can be customized in the application settings.
Users who are familiar with Twitter or Instagram will feel right at home with only having one option for "liking" a post. However, users from Facebook or other Nostr clients may wonder why they don't have more options for reactions. This is one of those things where users who are new to Nostr probably won't notice they are missing out on anything at all, while users familiar with clients like #Amethyst or #noStrudel will miss the ability to react with a 🤙 or a 🫂.
It's a similar story with the bookmark option. While this is a nice bit of feature parity for Twitter users, for those already used to the ability to have multiple customized lists of bookmarks, or at minimum have the ability to separate them into public and private, it may be a disappointment that they have no access to the bookmarks they already built up on other clients. Primal offers only one list of bookmarks for short-form notes and they are all visible to the public. However, you are at least presented with a warning about the public nature of your bookmarks before saving your first one.
Yet, I can't dock the Primal team much for making these design choices, as they are understandable for Primal's goal of being a welcoming client for those coming over to Nostr from centralized platforms. They have optimized for the onboarding of new users, rather than for those who have been around for a while, and there is absolutely nothing wrong with that.
Post Creation
Composing posts in Primal is as simple as it gets. Accessed by tapping the obvious circular button with a "+" on it in the lower right of the Home feed, most of what you could need is included in the interface, and nothing you don't.
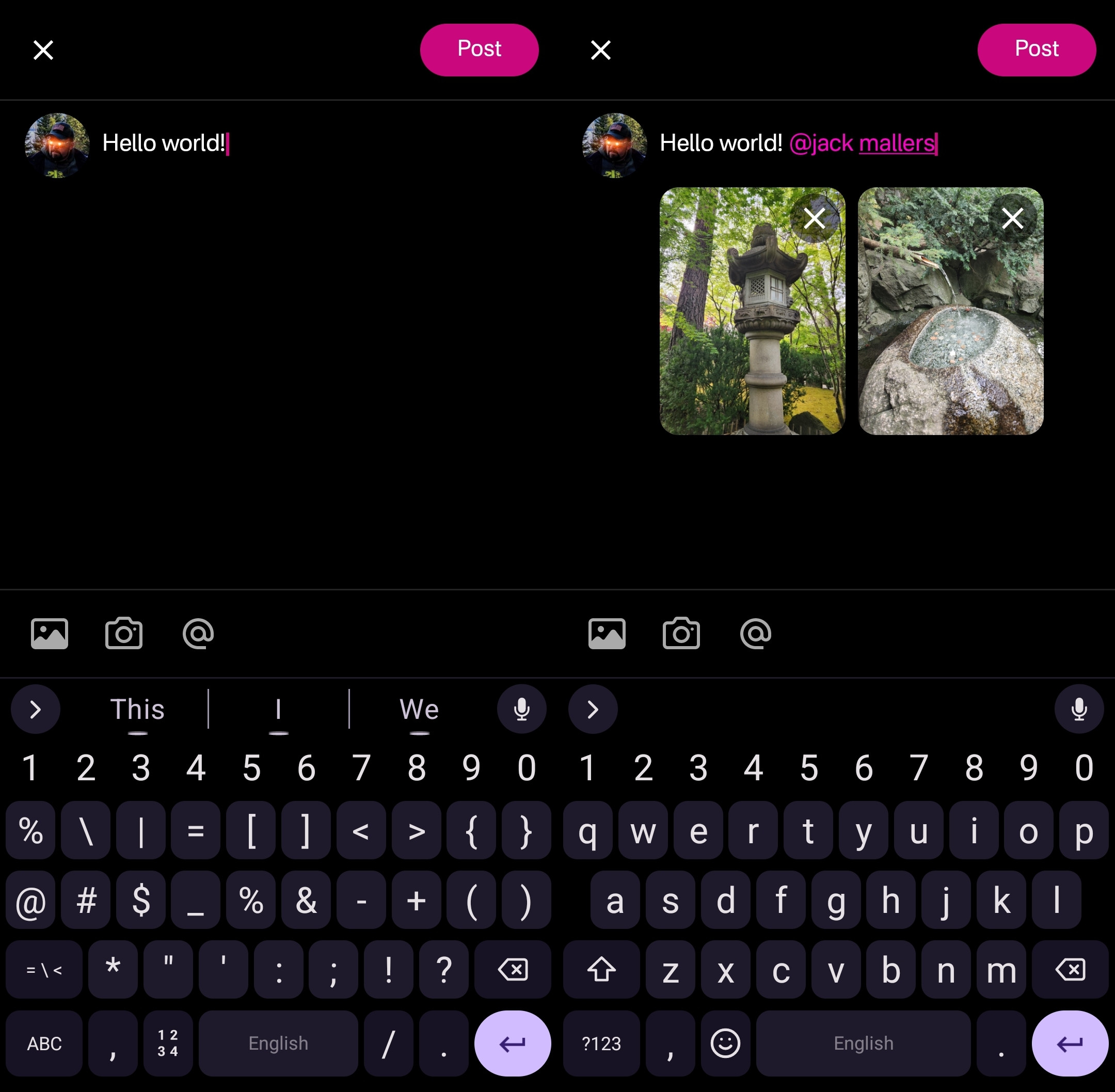
Your device's default keyboard loads immediately, and the you can start typing away.
There are options for adding images from your gallery, or taking a picture with your camera, both of which will result in the image being uploaded to Primal's media-hosting server. If you prefer to host your media elsewhere, you can simply paste the link to that media into your post.
There is also an @ icon as a tip-off that you can tag other users. Tapping on this simply types "@" into your note and brings up a list of users. All you have to do to narrow down the user you want to tag is continue typing their handle, Nostr address, or paste in their npub.
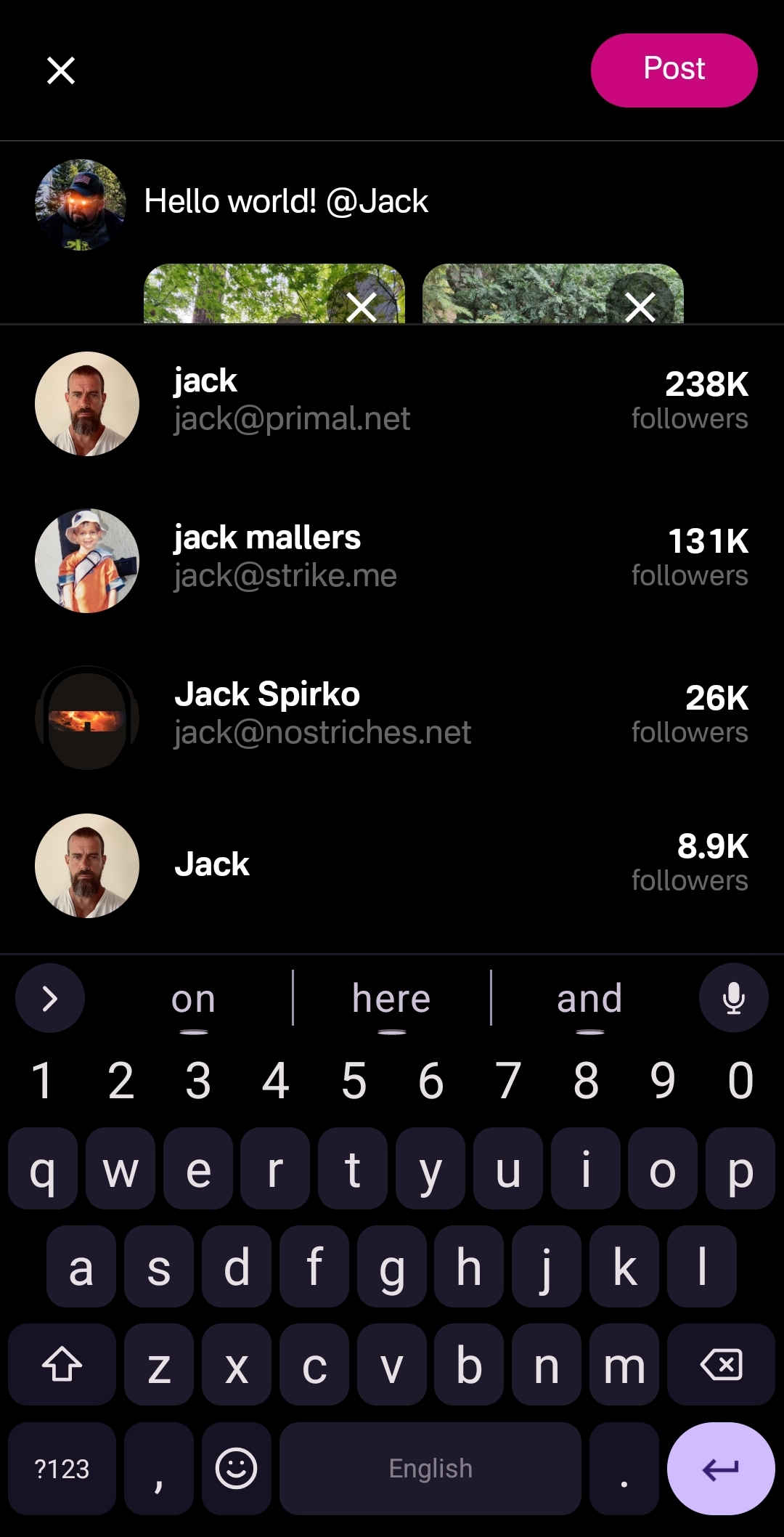
This can get mixed results in other clients, which sometimes have a hard time finding particular users when typing in their handle, forcing you to have to remember their Nostr address or go hunt down their npub by another means. Not so with Primal, though. I had no issues tagging anyone I wanted by simply typing in their handle.
Of course, when you are tagging someone well known, you may find that there are multiple users posing as that person. Primal helps you out here, though. Usually the top result is the person you want, as Primal places them in order of how many followers they have. This is quite reliable right now, but there is nothing stopping someone from spinning up an army of bots to follow their fake accounts, rendering follower count useless for determining which account is legitimate. It would be nice to see these results ranked by web-of-trust, or at least an indication of how many users you follow who also follow the users listed in the results.
Once you are satisfied with your note, the "Post" button is easy to find in the top right of the screen.
Feed Selector and Marketplace
Primal's Home feed really shines when you open up the feed selection interface, and find that there are a plethora of options available for customizing your view. By default, it only shows four options, but tapping "Edit" opens up a new page of available toggles to add to the feed selector.
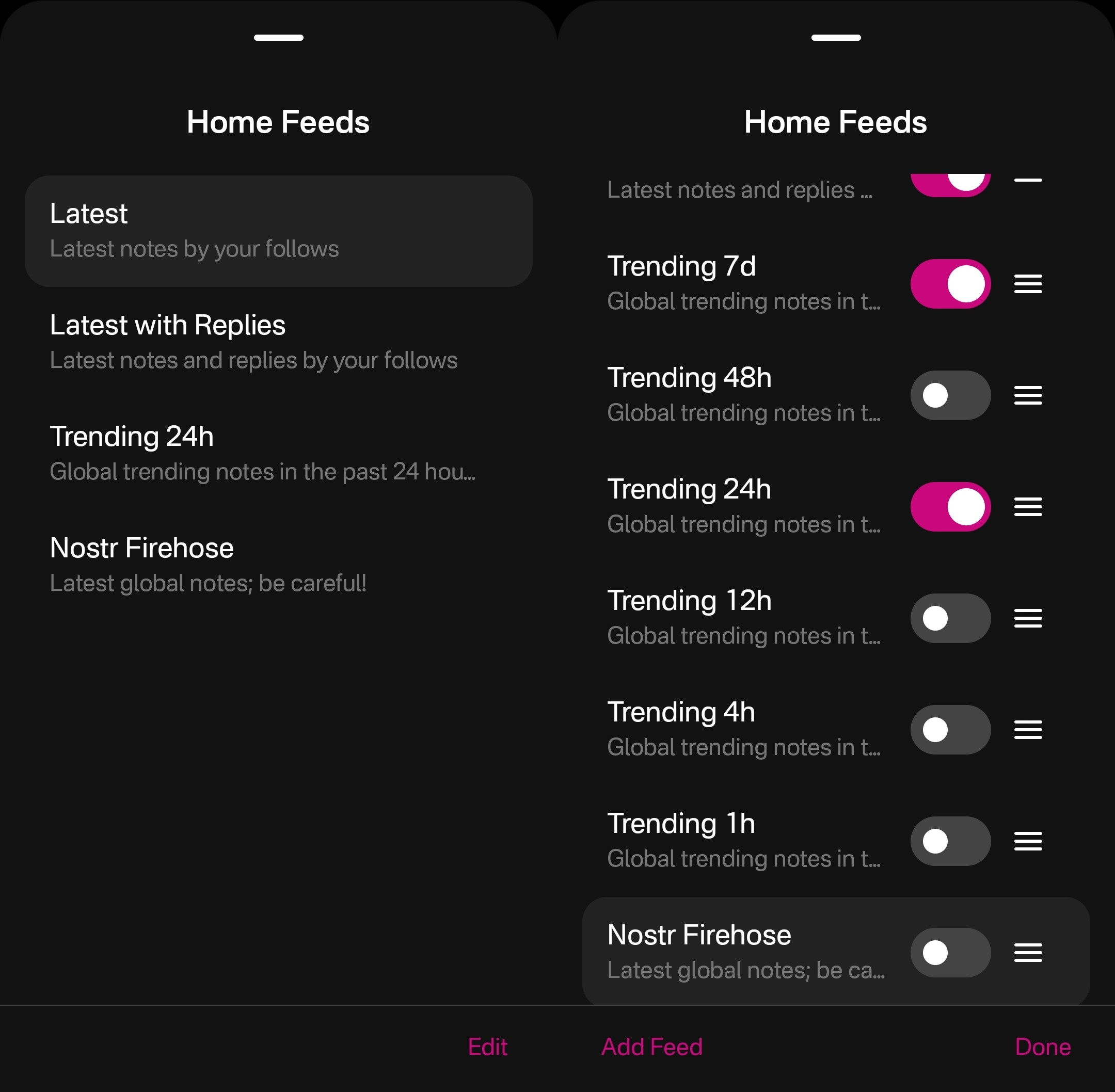
The options don't end there, though. Tapping "Add Feed" will open up the feed marketplace, where an ever-growing number of custom feeds can be found, some created by Primal and some created by others. This feed marketplace is available to a few other clients, but none have so closely integrated it with their Home feeds like Primal has.
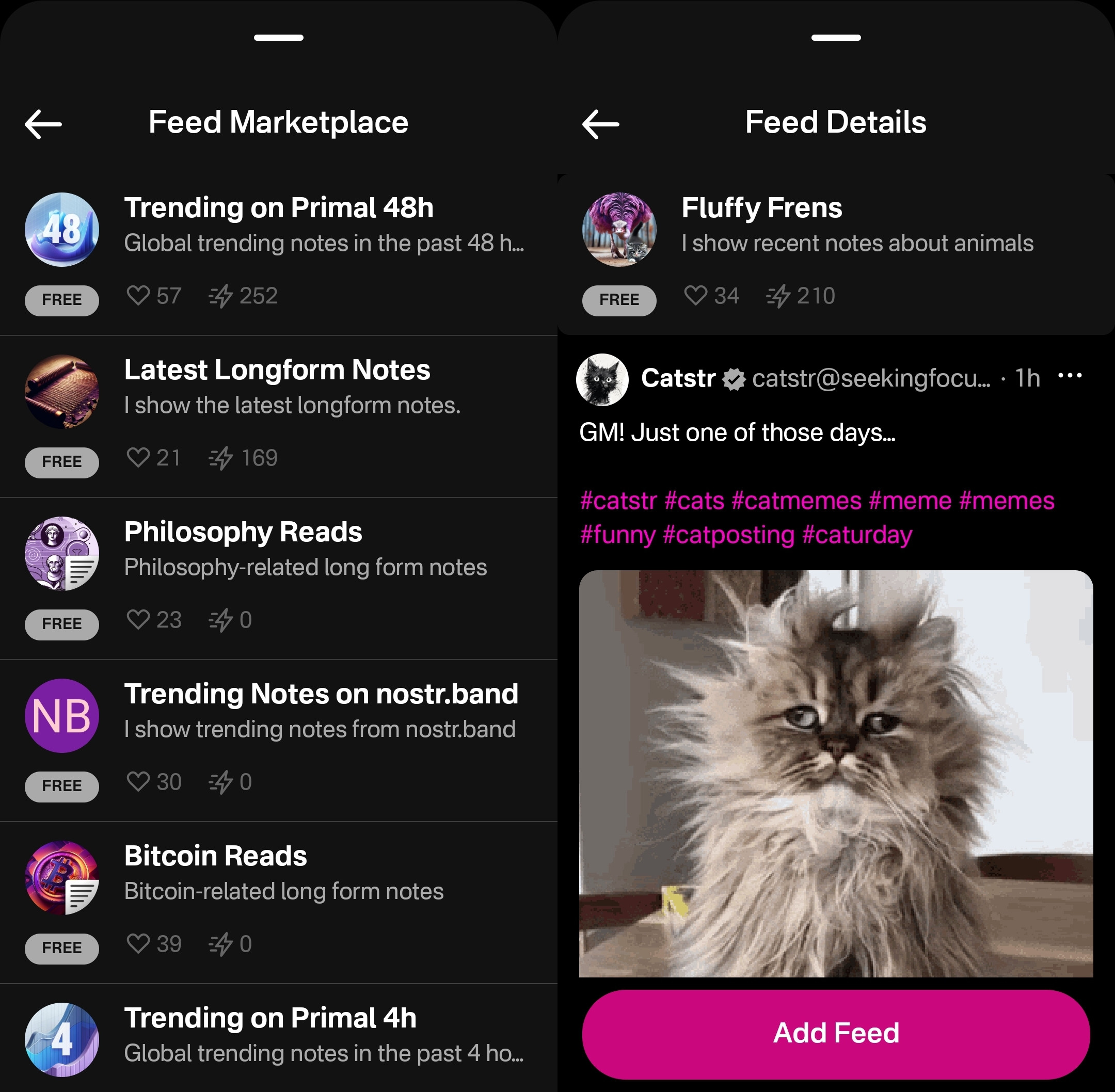
Unfortunately, as great as these custom feeds are, this was also the feature where I ran into the most bugs while testing out the app.
One of these bugs was while selecting custom feeds. Occasionally, these feed menu screens would become unresponsive and I would be unable to confirm my selection, or even use the back button on my device to back out of the screen. However, I was able to pull the screen down to close it and re-open the menu, and everything would be responsive again.
This only seemed to occur when I spent 30 seconds or more on the same screen, so I imagine that most users won't encounter it much in their regular use.
Another UI bug occurred for me while in the feed marketplace. I could scroll down the list of available feeds, but attempting to scroll back up the feed would often close the interface entirely instead, as though I had pulled the screen down from the top, when I was swiping in the middle of the screen.
The last of these bugs occurred when selecting a long-form "Reads" feed while in the menu for the Home feed. The menu would allow me to add this feed and select it to be displayed, but it would fail to load the feed once selected, stating "There is no content in this feed." Going to a different page within the the app and then going back to the Home tab would automatically remove the long-form feed from view, and reset back to the most recently viewed short-form "Notes" feed, though the long-form feed would still be available to select again. The results were similar when selecting a short-form feed for the Reads feed.
I would suggest that if long-form and short-form feeds are going to be displayed in the same list, and yet not be able to be displayed in the same feed, the application should present an error message when attempting to add a long-form feed for the Home feed or a short-form feed for the Reads feed, and encourage the user add it to the proper feed instead.
Long-Form "Reads" Feed
A brand new feature in Primal 2.0, users can now browse and read long-form content posted to Nostr without having to go to a separate client. Primal now has a dedicated "Reads" feed to browse and interact with these articles.
This feed displays the author and title of each article or blog, along with an image, if available. Quite conveniently, it also lets you know the approximate amount of time it will take to read a given article, so you can decide if you have the time to dive into it now, or come back later.
Noticeably absent from the Reads feed, though, is the ability to compose an article of your own. This is another understandable design choice for a mobile client. Composing a long-form note on a smart-phone screen is not a good time. Better to be done on a larger screen, in a client with a full-featured text editor.
Tapping an article will open up an attractive reading interface, with the ability to bookmark for later. These bookmarks are a separate list from your short-form note bookmarks so you don't have to scroll through a bunch of notes you bookmarked to find the article you told yourself you would read later and it's already been three weeks.
While you can comment on the article or zap it, you will notice that you cannot repost or quote-post it. It's not that you can't do so on Nostr. You absolutely can in other clients. In fact, you can do so on Primal's web client, too. However, Primal on Android does not handle rendering long-form note previews in the Home feed, so they have simply left out the option to share them there. See below for an example of a quote-post of a long-form note in the Primal web client vs the Android client.
Primal Web:
Primal Android:
The Explore Tab
Another unique feature of the Primal client is the Explore tab, indicated by the compass icon. This tab is dedicated to discovering content from outside your current follow list. You can find the feed marketplace here, and add any of the available feeds to your Home or Reads feed selections. You can also find suggested users to follow in the People tab. The Zaps tab will show you who has been sending and receiving large zaps. Make friends with the generous ones!
The Media tab gives you a chronological feed of just media, displayed in a tile view. This can be great when you are looking for users who post dank memes, or incredible photography on a regular basis. Unfortunately, it appears that there is no way to filter this feed for sensitive content, and so you do not have to scroll far before you see pornographic material.
Indeed, it does not appear that filters for sensitive content are available in Primal for any feed. The app is kind enough to give a minimal warning that objectionable content may be present when selecting the "Nostr Firehose" option in your Home feed, with a brief "be careful" in the feed description, but there is not even that much of a warning here for the media-only feed.
The media-only feed doesn't appear to be quite as bad as the Nostr Firehose feed, so there must be some form of filtering already taking place, rather than being a truly global feed of all media. Yet, occasional sensitive content still litters the feed and is unavoidable, even for users who would rather not see it. There are, of course, ways to mute particular users who post such content, if you don't want to see it a second time from the same user, but that is a never-ending game of whack-a-mole, so your only realistic choices in Primal are currently to either avoid the Nostr Firehose and media-only feeds, or determine that you can put up with regularly scrolling past often graphic content.
This is probably the only choice Primal has made that is not friendly to new users. Most clients these days will have some protections in place to hide sensitive content by default, but still allow the user to toggle those protections off if they so choose. Some of them hide posts flagged as sensitive content altogether, others just blur the images unless the user taps to reveal them, and others simply blur all images posted by users you don't follow. If Primal wants to target new users who are accustomed to legacy social media platforms, they really should follow suit.
The final tab is titled "Topics," but it is really just a list of popular hashtags, which appear to be arranged by how often they are being used. This can be good for finding things that other users are interested in talking about, or finding specific content you are interested in.
If you tap on any topic in the list, it will display a feed of notes that include that hashtag. What's better, you can add it as a feed option you can select on your Home feed any time you want to see posts with that tag.
The only suggestion I would make to improve this tab is some indication of why the topics are arranged in the order presented. A simple indicator of the number of posts with that hashtag in the last 24 hours, or whatever the interval is for determining their ranking, would more than suffice.
Even with those few shortcomings, Primal's Explore tab makes the client one of the best options for discovering content on Nostr that you are actually interested in seeing and interacting with.
Built-In Wallet
While this feature is completely optional, the icon to access the wallet is the largest of the icons at the bottom of the screen, making you feel like you are missing out on the most important feature of the app if you don't set it up. I could be critical of this design choice, but in many ways I think it is warranted. The built-in wallet is one of the most unique features that Primal has going for it.
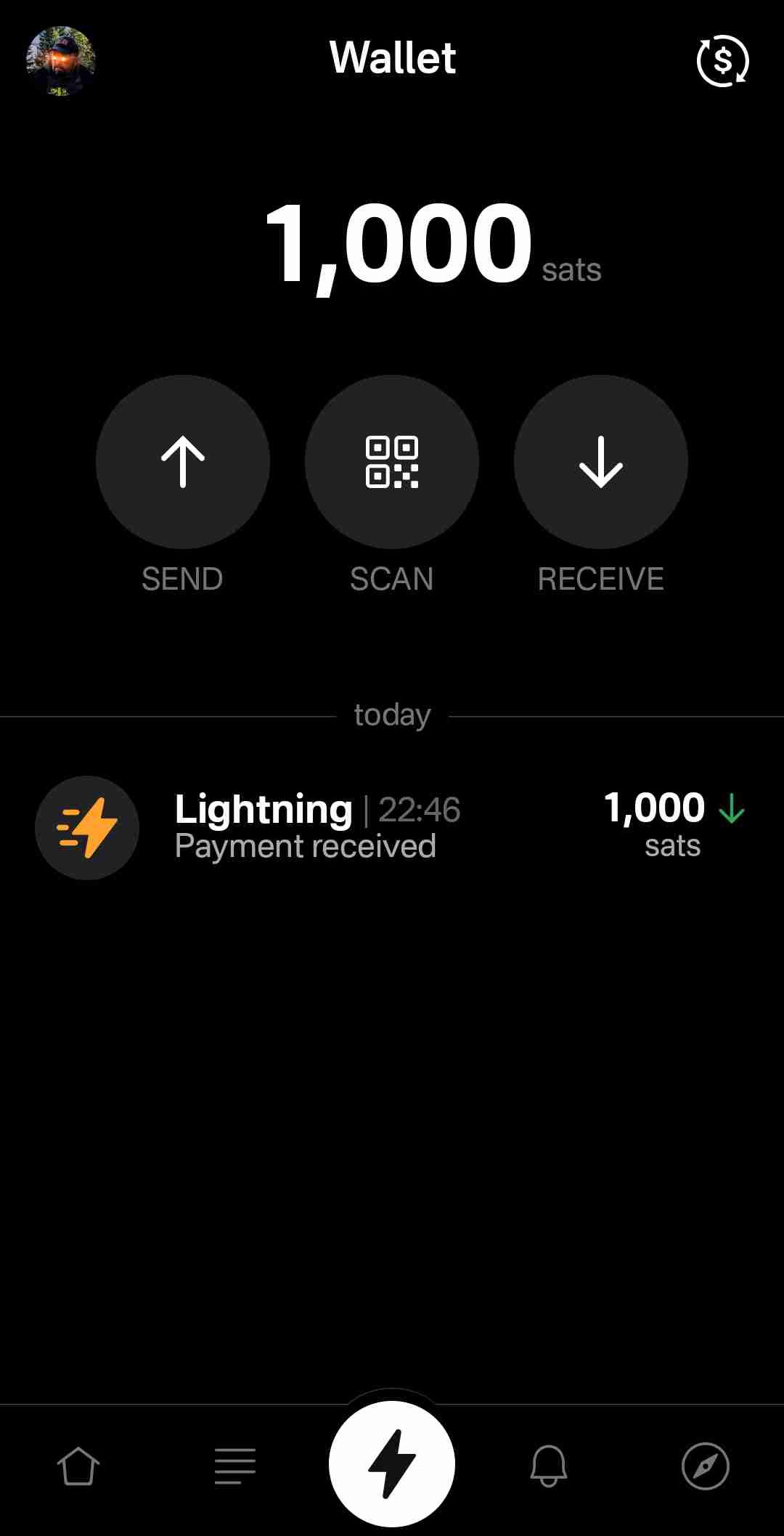
Consider: If you are a new user coming to Nostr, who isn't already a Bitcoiner, and you see that everyone else on the platform is sending and receiving sats for their posts, will you be more likely to go download a separate wallet application or use one that is built-into your client? I would wager the latter option by a long shot. No need to figure out which wallet you should download, whether you should do self-custody or custodial, or make the mistake of choosing a wallet with unexpected setup fees and no Lightning address so you can't even receive zaps to it. nostr:npub16c0nh3dnadzqpm76uctf5hqhe2lny344zsmpm6feee9p5rdxaa9q586nvr often states that he believes more people will be onboarded to Bitcoin through Nostr than by any other means, and by including a wallet into the Primal client, his team has made adopting Bitcoin that much easier for new Nostr users.
Some of us purists may complain that it is custodial and KYC, but that is an unfortunate necessity in order to facilitate onboarding newcoiners to Bitcoin. This is not intended to be a wallet for those of us who have been using Bitcoin and Lightning regularly already. It is meant for those who are not already familiar with Bitcoin to make it as easy as possible to get off zero, and it accomplishes this better than any other wallet I have ever tried.
In large part, this is because the KYC is very light. It does need the user's legal name, a valid email address, date of birth, and country of residence, but that's it! From there, the user can buy Bitcoin directly through the app, but only in the amount of $4.99 at a time. This is because there is a substantial markup on top of the current market price, due to utilizing whatever payment method the user has set up through their Google Play Store. The markup seemed to be about 19% above the current price, since I could purchase 4,143 sats for $4.99 ($120,415 / Bitcoin), when the current price was about $101,500. But the idea here is not for the Primal wallet to be a user's primary method of stacking sats. Rather, it is intended to get them off zero and have a small amount of sats to experience zapping with, and it accomplishes this with less friction than any other method I know.
Moreover, the Primal wallet has the features one would expect from any Lightning wallet. You can send sats to any Nostr user or Lightning address, receive via invoice, or scan to pay an invoice. It even has the ability to receive via on-chain. This means users who don't want to pay the markup from buying through Primal can easily transfer sats they obtained by other means into the Primal wallet for zapping, or for using it as their daily-driver spending wallet.
Speaking of zapping, once the wallet is activated, sending zaps is automatically set to use the wallet, and they are fast. Primal gives you immediate feedback that the zap was sent and the transaction shows in your wallet history typically before you can open the interface. I can confidently say that Primal wallet's integration is the absolute best zapping experience I have seen in any Nostr client.
One thing to note that may not be immediately apparent to new users is they need to add their Lightning address with Primal into their profile details before they can start receiving zaps. So, sending zaps using the wallet is automatic as soon as you activate it, but receiving is not. Ideally, this could be further streamlined, so that Primal automatically adds the Lightning address to the user's profile when the wallet is set up, so long as there is not currently a Lightning address listed.
Of course, if you already have a Lightning wallet, you can connect it to Primal for zapping, too. We will discuss this further in the section dedicated to zap integration.
Advanced Search
Search has always been a tough nut to crack on Nostr, since it is highly dependent on which relays the client is pulling information from. Primal has sought to resolve this issue, among others, by running a caching relay that pulls notes from a number of relays to store them locally, and perform some spam filtering. This allows for much faster retrieval of search results, and also makes their advanced search feature possible.
Advanced search can be accessed from most pages by selecting the magnifying glass icon, and then the icon for more options next to the search bar.
As can be seen in the screenshot below, there are a plethora of filters that can be applied to your search terms.
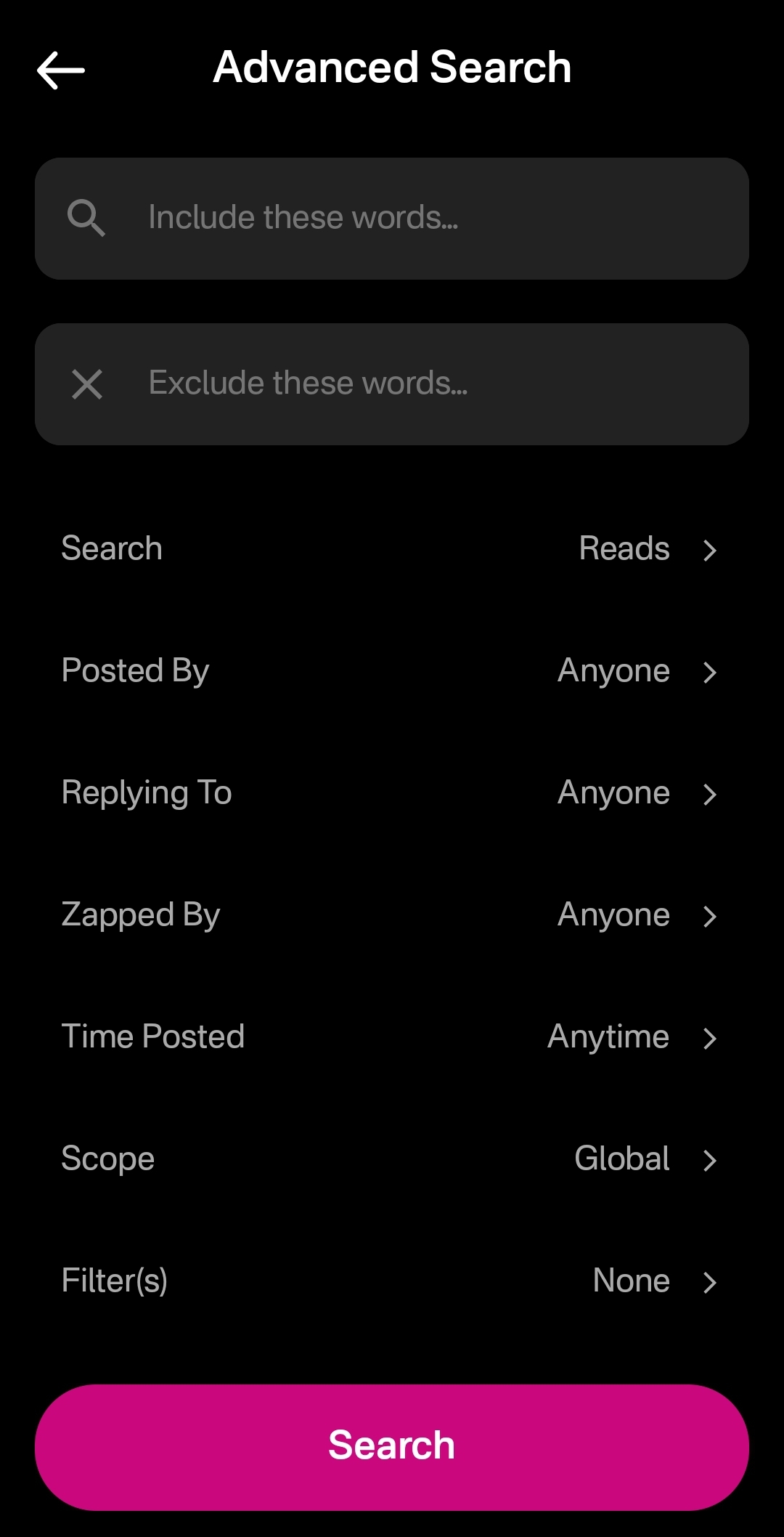
You can immediately see how this advanced search could be a very powerful tool for not just finding a particular previous note that you are looking for, but for creating your own custom feed of notes. Well, wouldn't you know it, Primal allows you to do just that! This search feature, paired with the other features mentioned above related to finding notes you want to see in your feed, makes Primal hands-down the best client for content discovery.
The only downside as a free user is that some of these search options are locked behind the premium membership. Or else you only get to see a certain number of results of your advanced search before you must be a premium member to see more.
Can My Grandma Use It?
Score: 4.8 / 5 Primal has obviously put a high priority on making their client user-friendly, even for those who have never heard of relays, public/private key cryptography, or Bitcoin. All of that complexity is hidden away. Some of it is available to play around with for the users who care to do so, but it does not at all get in the way of the users who just want to jump in and start posting notes and interacting with other users in a truly open public square.
To begin with, the onboarting experience is incredibly smooth. Tap "Create Account," enter your chosen display name and optional bio information, upload a profile picture, and then choose some topics you are interested in. You are then presented with a preview of your profile, with the ability to add a banner image, if you so choose, and then tap "Create Account Now."
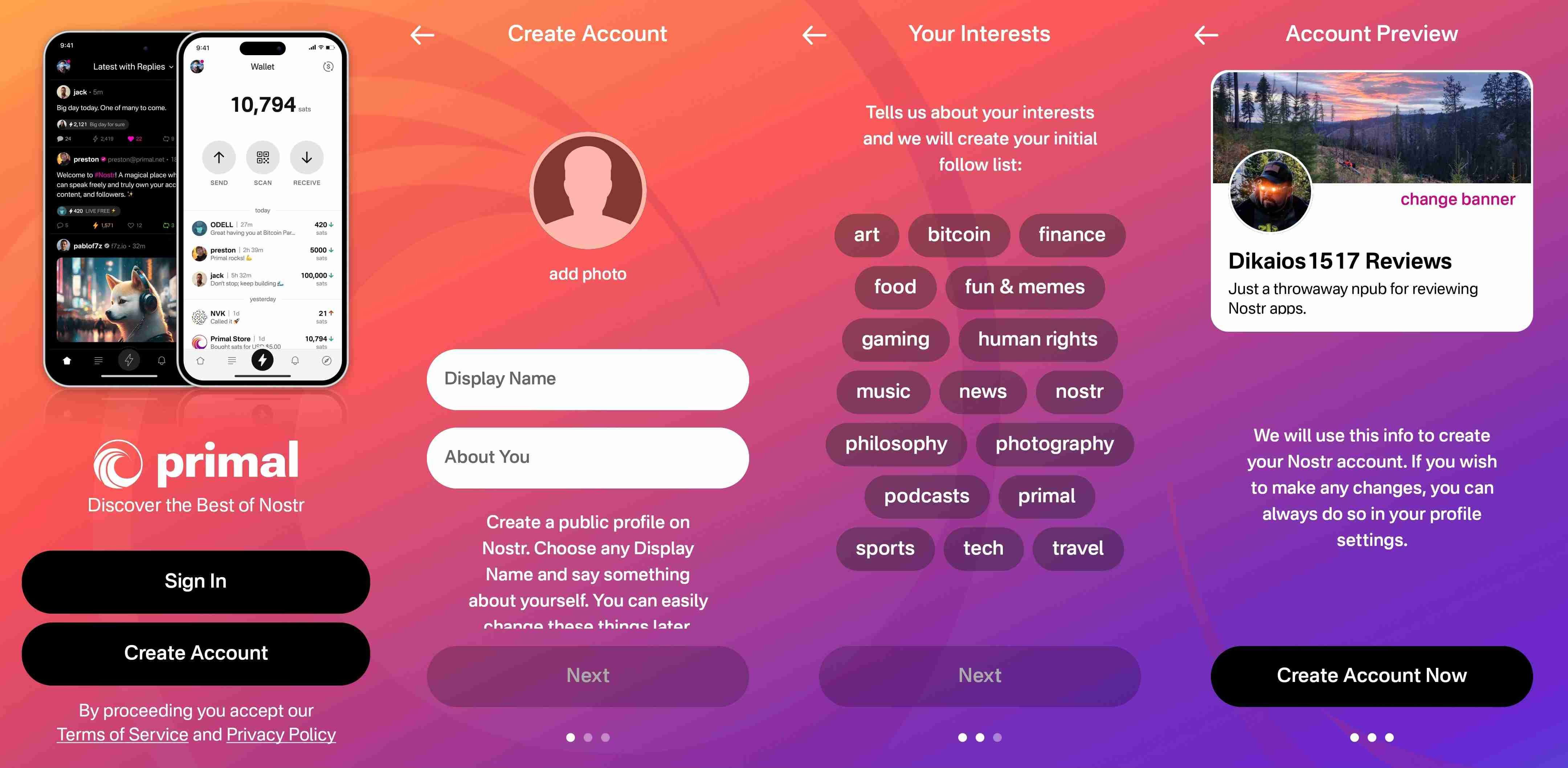
From there you receive confirmation that your account has been created and that your "Nostr key" is available to you in the application settings. No further explanation is given about what this key is for at this point, but the user doesn't really need to know at the moment, either. If they are curious, they will go to the app settings to find out.
At this point, Primal encourages the user to activate Primal Wallet, but also gives the option for the user to do it later.
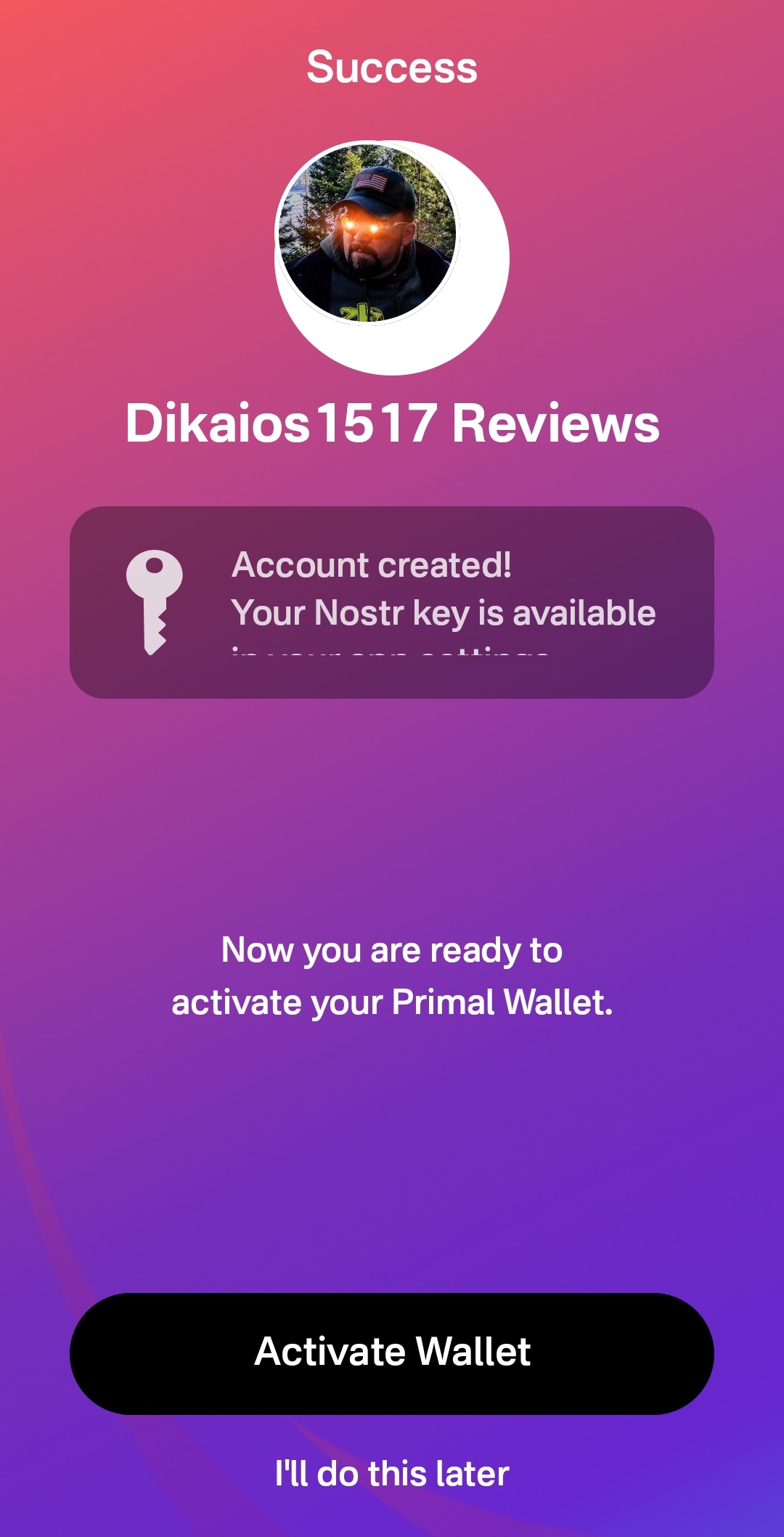
That's it! The next screen the user sees if they don't opt to set up the wallet is their Home feed with notes listed in chronological order. More impressive, the feed is not empty, because Primal has auto-followed several accounts based on your selected topics.
Now, there has definitely been some legitimate criticism of this practice of following specific accounts based on the topic selection, and I agree. I would much prefer to see Primal follow hashtags based on what was selected, and combine the followed hashtags into a feed titled "My Topics" or something of that nature, and make that the default view when the user finishes onboarding. Following particular users automatically will artificially inflate certain users' exposure, while other users who might be quality follows for that topic aren't seen at all.
The advantage of following particular users over a hashtag, though, is that Primal retains some control over the quality of the posts that new users are exposed to right away. Primal can ensure that new users see people who are actually posting quality photography when they choose it as one of their interests. However, even with that example, I chose photography as one of my interests and while I did get some stunning photography in my Home feed by default based on Primal's chosen follows, I also scrolled through the Photography hashtag for a bit and I really feel like I would have been better served if Primal had simply followed that hashtag rather than a particular set of users.
We've already discussed how simple it is to set up the Primal Wallet. You can see the features section above if you missed it. It is, by far, the most user friendly experience to onboarding onto Lightning and getting a few sats for zapping, and it is the only one I know of that is built directly into a Nostr client. This means new users will have a frictionless introduction to transacting via Lightning, perhaps without even realizing that's what they are doing.
Discovering new content of interest is incredibly intuitive on Primal, and the only thing that new users may struggle with is getting their own notes seen by others. To assist with this, I would suggest Primal encourage users to make their first post to the introductions hashtag and direct any questions to the AskNostr hashtag as part of the onboarding process. This will get them some immediate interactions from other users, and further encouragement to set up their wallet if they haven't already done so.
How do UI look?
Score: 4.9 / 5
Primal is the most stunningly beautiful Nostr client available, in my honest opinion. Despite some of my hangups about certain functionality, the UI alone makes me want to use it.
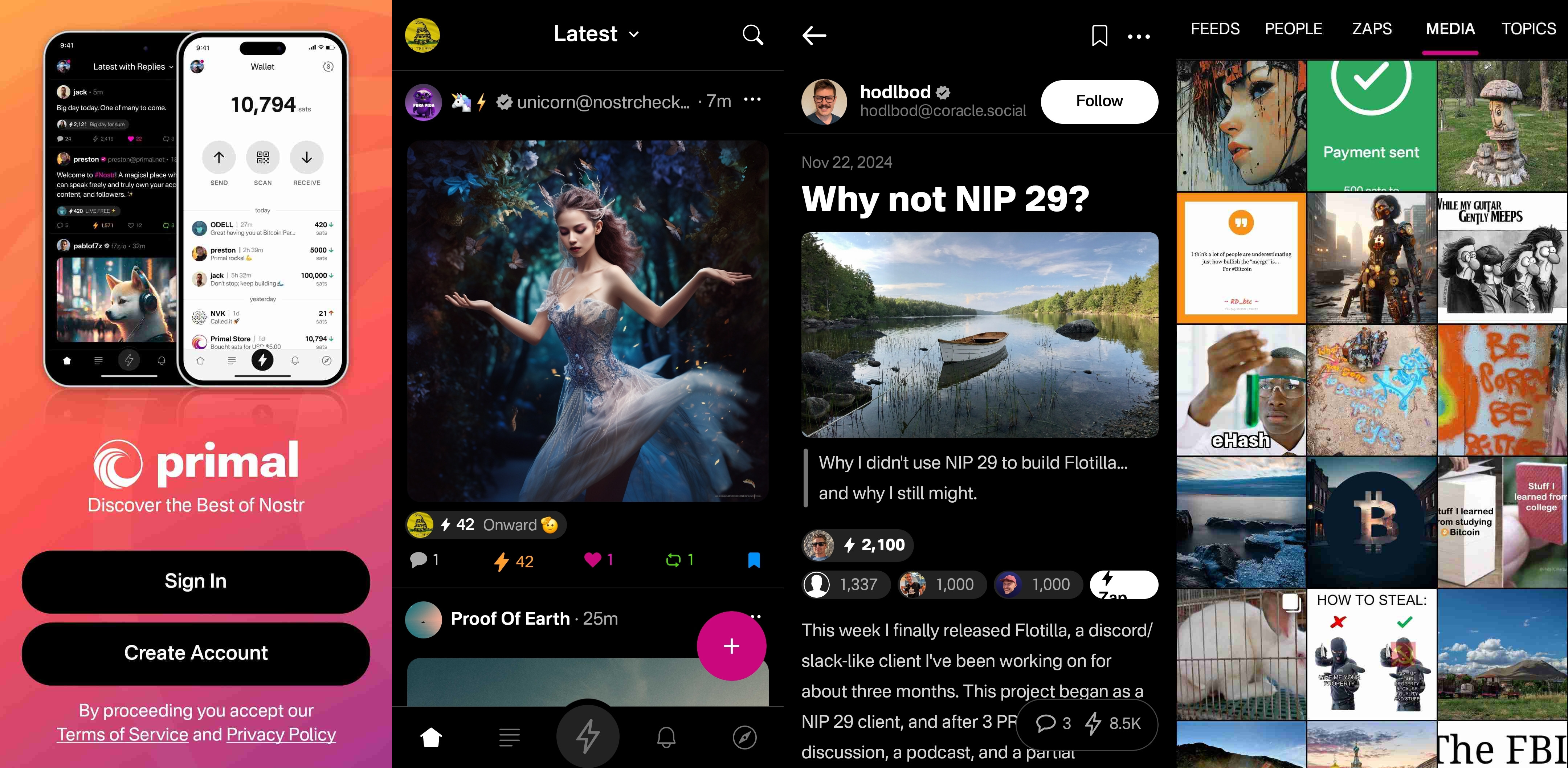
It is clean, attractive, and intuitive. Everything I needed was easy to find, and nothing felt busy or cluttered. There are only a few minor UI glitches that I ran into while testing the app. Some of them were mentioned in the section of the review detailing the feed selector feature, but a couple others occurred during onboarding.
First, my profile picture was not centered in the preview when I uploaded it. This appears to be because it was a low quality image. Uploading a higher quality photo did not have this result.

The other UI bug was related to text instructions that were cut off, and not able to scroll to see the rest of them. This occurred on a few pages during onboarding, and I expect it was due to the size of my phone screen, since it did not occur when I was on a slightly larger phone or tablet.
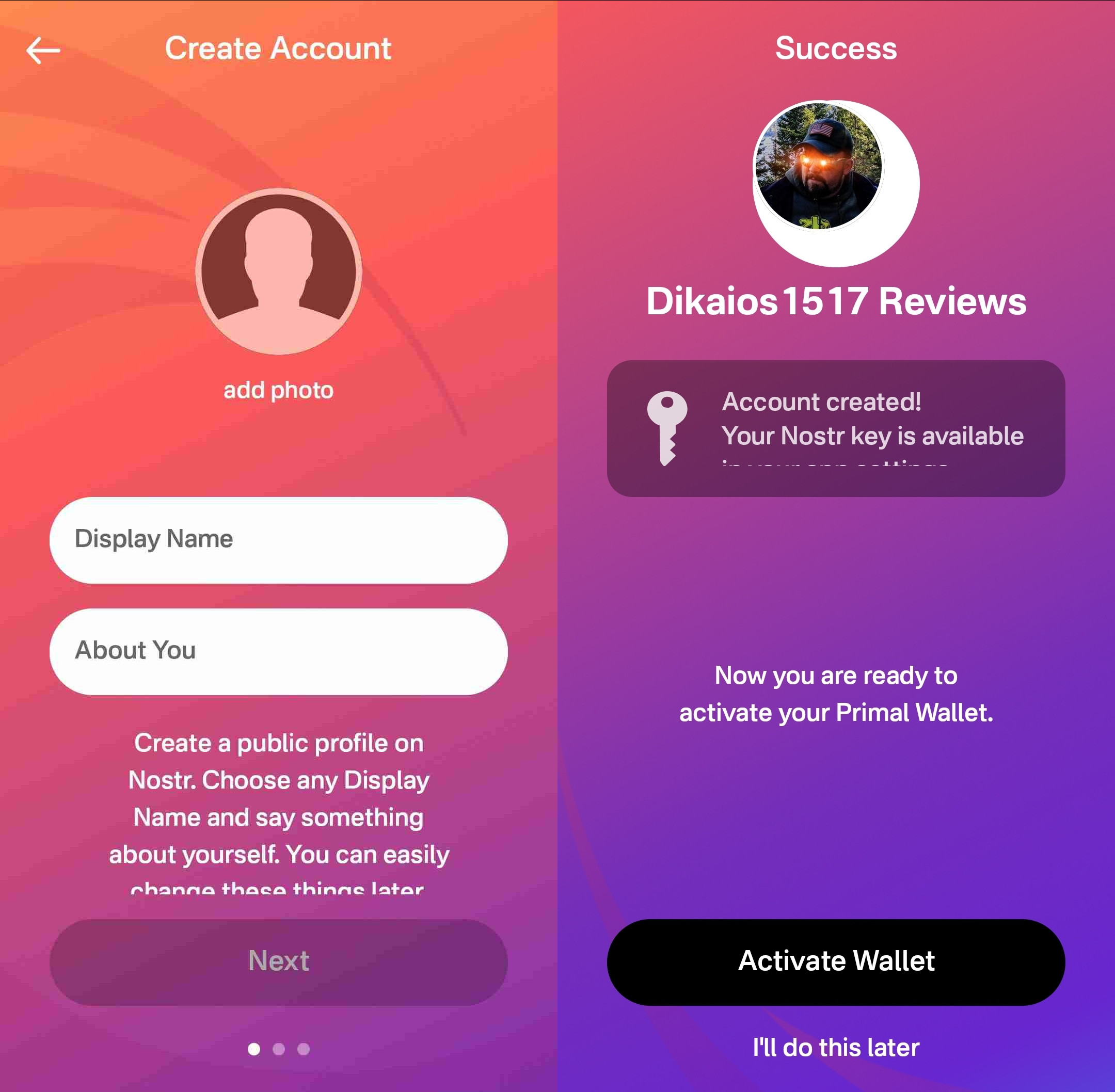
Speaking of tablets, Primal Android looks really good on a tablet, too! While the client does not have a landscape mode by default, many Android tablets support forcing apps to open in full-screen landscape mode, with mixed results. However, Primal handles it well. I would still like to see a tablet version developed that takes advantage of the increased screen real estate, but it is certainly a passable option.

At this point, I would say the web client probably has a bit better UI for use on a tablet than the Android client does, but you miss out on using the built-in wallet, which is a major selling point of the app.
This lack of a landscape mode for tablets and the few very minor UI bugs I encountered are the only reason Primal doesn't get a perfect score in this category, because the client is absolutely stunning otherwise, both in light and dark modes. There are also two color schemes available for each.
Log In Options
Score: 1 / 5
Unfortunately, Primal has not included any options for log in outside of pasting your private key into the application. While this is a very simple way to log in for new users to understand, it is also the least secure means to log into Nostr applications.
This is because, even with the most trustworthy client developer, giving the application access to your private key always has the potential for that private key to somehow be exposed or leaked, and on Nostr there is currently no way to rotate to a different private key and keep your identity and social graph. If someone gets your key, they are you on Nostr for all intents and purposes.
This is not a situation that users should be willing to tolerate from production-release clients at this point. There are much better log in standards that can and should be implemented if you care about your users.
That said, I am happy to report that external signer support is on the roadmap for Primal, as confirmed below:
nostr:note1n59tc8k5l2v30jxuzghg7dy2ns76ld0hqnn8tkahyywpwp47ms5qst8ehl
No word yet on whether this will be Android signer or remote signer support, or both.
This lack of external signer support is why I absolutely will not use my main npub with Primal for Android. I am happy to use the web client, which supports and encourages logging in with a browser extension, but until the Android client allows users to protect their private key, I cannot recommend it for existing Nostr users.
Zap Integration
Score: 4.8 / 5
As mentioned when discussing Primal's built-in wallet feature, zapping in Primal can be the most seamless experience I have ever seen in a Nostr client. Pairing the wallet with the client is absolutely the path forward for Nostr leading the way to Bitcoin adoption.
But what if you already have a Lightning wallet you want to use for zapping? You have a couple options. If it is an Alby wallet or another wallet that supports Nostr Wallet Connect, you can connect it with Primal to use with one-tap zapping.
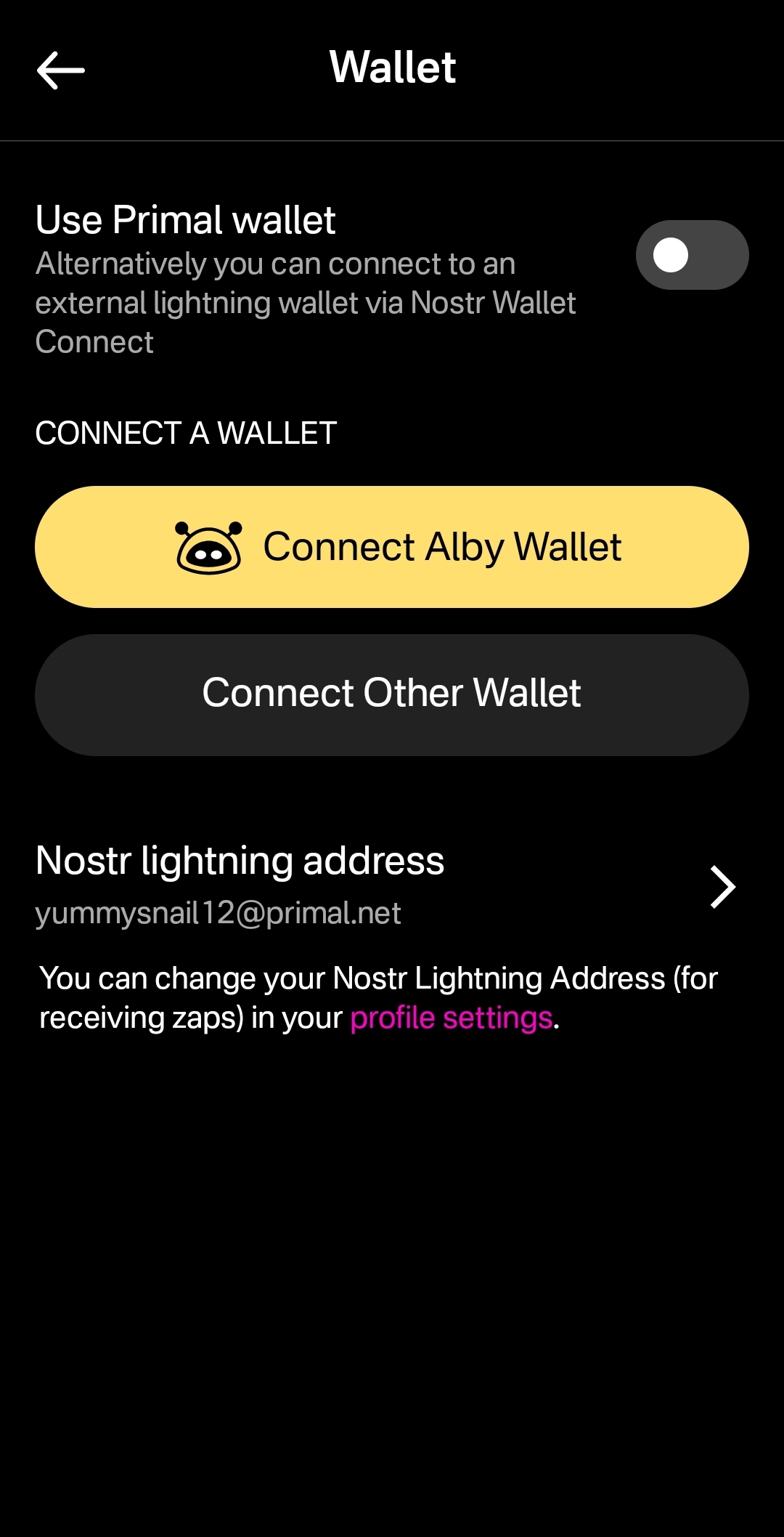
How your zapping experience goes with this option will vary greatly based on your particular wallet of choice and is beyond the scope of this review. I used this option with a hosted wallet on my Alby Hub and it worked perfectly. Primal gives you immediate feedback that you have zapped, even though the transaction usually takes a few seconds to process and appear in your wallet's history.
The one major downside to using an external wallet is the lack of integration with the wallet interface. This interface currently only works with Primal's wallet, and therefore the most prominent tab in the entire app goes unused when you connect an external wallet.
An ideal improvement would be for the wallet screen to work similar to Alby Go when you have an external wallet connected via Nostr Wallet Connect, allowing the user to have Primal act as their primary mobile Lightning wallet. It could have balance and transaction history displayed, and allow sending and receiving, just like the integrated Primal wallet, but remove the ability to purchase sats directly through the app when using an external wallet.
Content Discovery
Score: 4.8 / 5
Primal is the best client to use if you want to discover new content you are interested in. There is no comparison, with only a few caveats.
First, the content must have been posted to Nostr as either a short-form or long-form note. Primal has a limited ability to display other types of content. For instance, discovering video content or streaming content is lacking.
Second, you must be willing to put up with the fact that Primal lacks a means of filtering sensitive content when you are exploring beyond the bounds of your current followers. This may not be an issue for some, but for others it could be a deal-breaker.
Third, it would be preferable for Primal to follow topics you are interested in when you choose them during onboarding, rather than follow specific npubs. Ideally, create a "My Topics" feed that can be edited by selecting your interests in the Topics section of the Explore tab.
Relay Management
Score: 2.5 / 5
For new users who don't want to mess around with managing relays, Primal is fantastic! There are 7 relays selected by default, in addition to Primal's caching service. For most users who aren't familiar with Nostr's protocol archetecture, they probably won't ever have to change their default relays in order to use the client as they would expect.
However, two of these default relays were consistently unreachable during the week that I tested. These were relay.plebes.fans and remnant.cloud. The first relay seems to be an incorrect URL, as I found nosflare.plebes.fans online and with perfect uptime for the last 12 hours on nostr.watch. I was unable to find remnant.cloud on nostr.watch at all. A third relay was intermittent, sometimes online and reachable, and other times unreachable: v1250.planz.io/nostr. If Primal is going to have default relays, they should ideally be reliable and with accurate URLs.
That said, users can add other relays that they prefer, and remove relays that they no longer want to use. They can even set a different caching service to use with the client, rather than using Primal's.
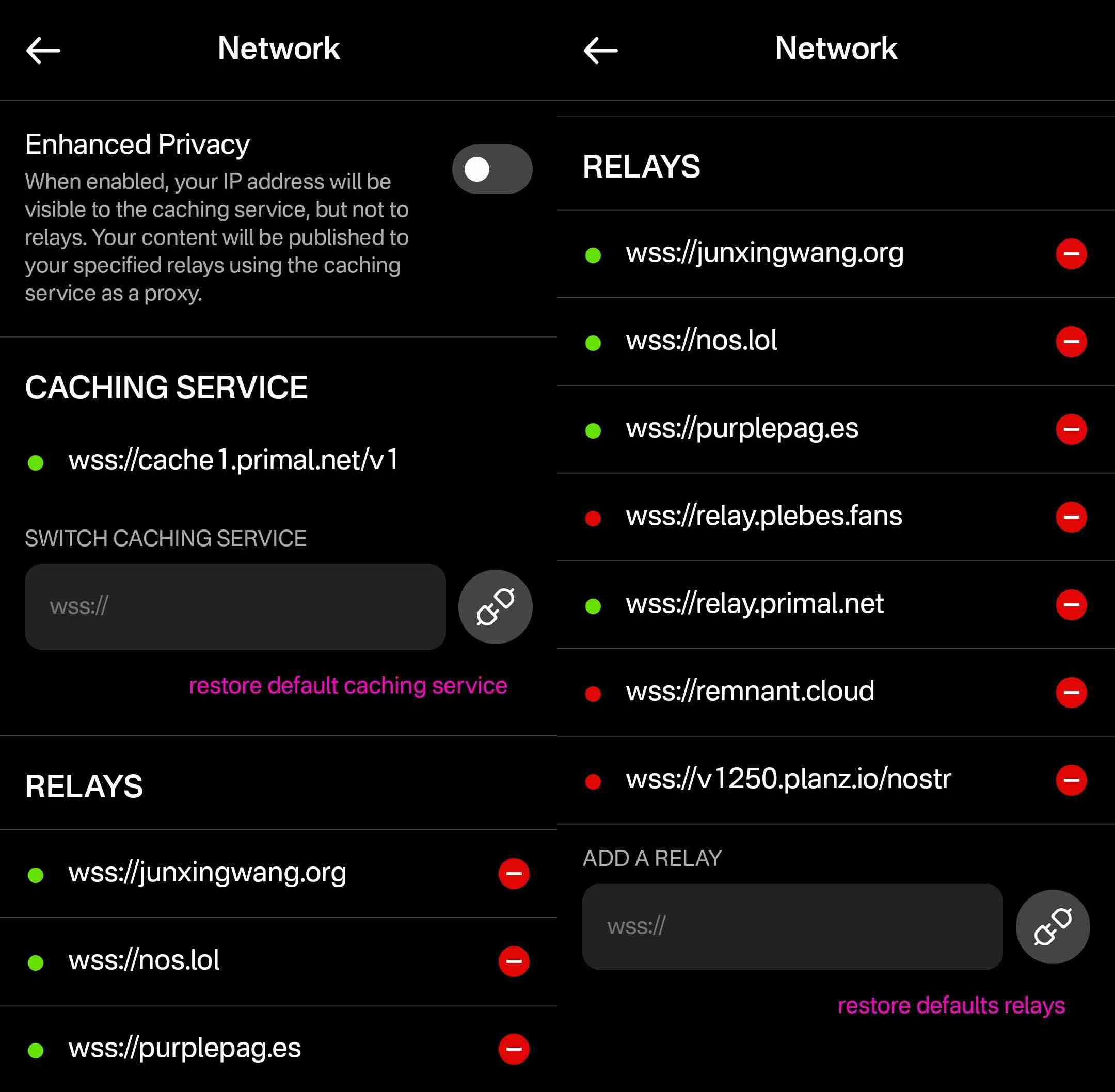
However, that is the extent of a user's control over their relays. They cannot choose which relays they want to write to and which they want to read from, nor can they set any private relays, outbox or inbox relays, or general relays. Loading the npub I used for this review into another client with full relay management support revealed that the relays selected in Primal are being added to both the user's public outbox relays and public inbox relays, but not to any other relay type, which leads me to believe the caching relay is acting as the client's only general relay and search relay.
One unique and welcomed addition is the "Enhanced Privacy" feature, which is off by default, but which can be toggled on. I am not sure why this is not on by default, though. Perhaps someone from the Primal team can enlighten me on that choice.
By default, when you post to Nostr, all of your outbox relays will see your IP address. If you turn on the Enhanced Privacy mode, only Primal's caching service will see your IP address, because it will post your note to the other relays on your behalf. In this way, the caching service acts similar to a VPN for posting to Nostr, as long as you trust Primal not to log or leak your IP address.
Current Users' Questions
The AskNostr hashtag can be a good indication of the pain points that other users are currently having with a client. Here are some of the most common questions submitted about Primal since the launch of 2.0:
nostr:note1dqv4mwqn7lvpaceg9s7damf932ydv9skv2x99l56ufy3f7q8tkdqpxk0rd
This was a pretty common question, because users expect that they will be able to create the same type of content that they can consume in a particular client. I can understand why this was left out in a mobile client, but perhaps it should be added in the web client.
nostr:note16xnm8a2mmrs7t9pqymwjgd384ynpf098gmemzy49p3572vhwx2mqcqw8xe
This is a more concerning bug, since it appears some users are experiencing their images being replaced with completely different images. I did not experience anything similar in my testing, though.
nostr:note1uhrk30nq0e566kx8ac4qpwrdh0vfaav33rfvckyvlzn04tkuqahsx8e7mr
There hasn't been an answer to this, but I have not been able to find a way. It seems search results will always include replies as well as original notes, so a feed made from the search results will as well. Perhaps a filter can be added to the advanced search to exclude replies? There is already a filter to only show replies, but there is no corresponding filter to only show original notes.
nostr:note1zlnzua28a5v76jwuakyrf7hham56kx9me9la3dnt3fvymcyaq6eqjfmtq6
Since both mobile platforms support the wallet, users expect that they will be able to access it in their web client, too. At this time, they cannot. The only way to have seamless zapping in the web client is to use the Alby extension, but there is not a way to connect it to your Primal wallet via Nostr Wallet Connect either. This means users must have a separate wallet for zapping on the web client if they use the Primal Wallet on mobile.
nostr:note15tf2u9pffy58y9lk27y245ew792raqc7lc22jezxvqj7xrak9ztqu45wep
It seems that Primal is filtering for spam even for profiles you actively follow. Moreover, exactly what the criteria is for being considered spam is currently opaque.
nostr:note1xexnzv0vrmc8svvduurydwmu43w7dftyqmjh4ps98zksr39ln2qswkuced
For those unaware, Blossom is a protocol for hosting media as blobs identified by a hash, allowing them to be located on and displayed from other servers they have been mirrored to when when the target server isn't available. Primal currently runs a Blossom server (blossom.primal.net) so I would expect we see Blossom support in the future.
nostr:note1unugv7s36e2kxl768ykg0qly7czeplp8qnc207k4pj45rexgqv4sue50y6
Currently, Primal on Android only supports uploading photos to your posts. Users must upload any video to some other hosting service and copy/paste a link to the video into their post on Primal. I would not be surprised to see this feature added in the near future, though.
nostr:note10w6538y58dkd9mdrlkfc8ylhnyqutc56ggdw7gk5y7nsp00rdk4q3qgrex
Many Nostr users have more than one npub for various uses. Users would prefer to have a way to quickly switch between accounts than to have to log all the way out and paste their npub for the other account every time they want to use it.
There is good news on this front, though:
nostr:note17xv632yqfz8nx092lj4sxr7drrqfey6e2373ha00qlq8j8qv6jjs36kxlh
Wrap Up
All in all, Primal is an excellent client. It won't be for everyone, but that's one of the strengths of Nostr as a protocol. You can choose to use the client that best fits your own needs, and supplement with other clients and tools as necessary.
There are a couple glaring issues I have with Primal that prevent me from using it on my main npub, but it is also an ever-improving client, that already has me hopeful for those issues to be resolved in a future release.
So, what should I review next? Another Android client, such as #Amethyst or #Voyage? Maybe an "other stuff" app, like #Wavlake or #Fountain? Please leave your suggestions in the comments.
I hope this review was valuable to you! If it was, please consider letting me know just how valuable by zapping me some sats and reposting it out to your follows.
Thank you for reading!
PV 🤙
-
 @ 878dff7c:037d18bc
2025-03-06 06:49:59
@ 878dff7c:037d18bc
2025-03-06 06:49:59Overview
Cyclone Alfred, currently a Category 2 storm, is approaching Australia's east coast, particularly targeting Queensland and northern New South Wales. The cyclone's landfall has been delayed, now anticipated between Friday and Saturday. Authorities have implemented extensive safety measures, including closing schools, halting public transport, and issuing evacuation orders. Residents are advised to prepare for heavy rainfall, strong winds, and potential flooding.
(Photo courtesy of Sean. Thanks Sean, it was the only on-location photo you sent ;). Stay safe!)
Resources
TROPICAL CYCLONE FORECAST TRACK MAP
Redland City Council Emergency Dashboard - Thanks Michael! Stay safe!
News
Lismore Braces for Major Flooding as Cyclone Alfred Approaches
Summary:
Lismore is on high alert for potential major flooding due to Cyclone Alfred. Water levels have already reached 1.23 meters even before the cyclone's full impact. NSW Premier Chris Minns described the cyclone as an "unwanted house guest," warning of extended damages from heavy rains and strong winds. Over 2,000 SES volunteers and various emergency services are deployed to ensure public safety, with 24 areas under 'prepare to evacuate' orders. Mayor Steve Krieg acknowledged the community's trauma from the 2022 floods but praised early preparations. Councillor Harper Dalton-Earls noted the community's improved preparedness, though concerns over the buyback process and flood-proofing strategies remain. Authorities emphasize the importance of heeding warnings and taking safety measures ahead of the storm.
Sources: The Daily Telegraph - March 6, 2025
Schools Closed and Public Transport Halted as Cyclone Alfred Nears
Summary:
Tropical Cyclone Alfred is approaching the eastern coast of Queensland, bringing strong winds and heavy rain. Brisbane is expected to experience significant impacts, including potential widespread flooding, as the cyclone is predicted to become the first to hit the area since 1974. Authorities have taken precautionary measures by shutting down 940 schools and halting public transportation. Residents are stocking up on essentials, and a shortage of sandbags has led to the use of potting mix as an alternative. With winds already affecting parts of the coast and rivers rising, emergency teams are preparing for potential evacuations. The prime minister reassured that the government is ready to support affected regions, as strong winds and high tides continue to pose challenges.
Sources: Associated Press - March 6, 2025
Trio on Jet Ski Rescued Amid Cyclone Alfred's Rough Conditions
Summary:
Three individuals on a jet ski sparked an extensive rescue operation near Noosa North Shore, Queensland, after becoming stranded in rough conditions and activating a flare. The rescue involved the Noosa Coast Guard and lifeguards who faced challenging weather due to Cyclone Alfred's approach. Despite the dangerous situation, the trio was safely retrieved, with two being brought back by a lifeguard and the third by the coast guard. The Noosa Coast Guard Flotilla Commander criticized the decision to venture out during the cyclone warning, noting that none of them had mobile phones for communication. Fortunately, all three individuals were unharmed. Separately, a man in his 60s suffered a significant arm injury after falling from a roof onto a pool fence at Little Cove, Noosa, and was taken to Sunshine Coast University Hospital in stable condition.
Sources: The Courier-Mail - March 6, 2025
Adelaide Flights Grounded as Cyclone Alfred Approaches Queensland
Summary:
Numerous Adelaide flights to and from Brisbane have been grounded due to the approach of Tropical Cyclone Alfred. Only a few morning departures and afternoon arrivals are proceeding on Thursday. Adelaide Airport confirmed the cancellation of all flights departing for Brisbane after 10:10 am and all arrivals from Brisbane after 4:20 pm. This follows an earlier announcement canceling all flights between Adelaide and Gold Coast for the day. Passengers are advised to check with their airlines for updates regarding Friday flights. Virgin Australia is offering free rescheduling within 14 days for affected travelers, and Qantas and Jetstar passengers are being offered travel credits and fee waivers for date changes. The cyclone, the first to hit the region in 50 years, may strengthen before making landfall late Friday or Saturday morning. Travelers are advised to monitor the situation closely and contact airlines if impacted.
Sources: The Advertiser - March 6, 2025
Over 265 Schools Closed in Northern NSW as Cyclone Alfred Intensifies
Summary:
Cyclone Alfred is set to bring severe weather to Northern NSW, prompting the closure of over 265 schools, including public, Catholic, and independent schools, as well as TAFE campuses. The Bureau of Meteorology has predicted gale-force winds, damaging gusts, and potential storm surges which could lead to dangerous flooding. Residents have been advised to prepare for evacuation, especially in low-lying areas, with potential rainfall up to 400mm and winds reaching 150km/h. State Emergency Operations Controller Peter Thurtell emphasized the seriousness of the situation, urging caution. Education Minister Prue Car stated that the school closures, effective through Friday, prioritize safety despite not being an easy decision. As the cyclone may intensify to a Category 3 before landfall in South East Queensland, authorities are actively monitoring for updates and preparing evacuation centers.
Sources: The Daily Telegraph - March 6, 2025
Residents Capture Dramatic Footage as Cyclone Alfred Approaches
Summary:
A dramatic video shared on TikTok shows water inundating Currumbin Alley south of Palm Beach due to Tropical Cyclone Alfred, which has caused flash floods sweeping away cars and crossing roads. Residents of the Gold Coast are preparing for the cyclone's arrival, anticipated to reach category two by Friday or Saturday. However, some people still visit the iconic beaches despite authorities' warnings about dangerous conditions. A 12.3-meter wave, the highest recorded, has been monitored. A 78-year-old woman was swept by a large wave and suffered a head injury, being transported to Gold Coast University Hospital. Acting Mayor Donna Gates has urged residents to stay away from the beaches due to the risks posed by Cyclone Alfred.
Sources: news.com.au - March 6, 2025
Concerns Rise as Cyclone Alfred Slows Down, Potentially Strengthening
Summary:
Tropical Cyclone Alfred, currently a category 2 storm, has slowed down and is traveling westwards at 10 km/h. Initially expected to make landfall late Thursday, it is now forecasted to hit the Queensland coast early Saturday morning. There are concerns it could strengthen to category 3. Significant impacts are already being felt from Coolangatta to Ballina, NSW. Evacuation centers are opening, schools and public transport are shut down, and grocery stores in affected areas of Queensland will close starting Thursday. Authorities remain vigilant as they continue to monitor the situation.
Sources: news.com.au - March 6, 2025
Flight Suspensions in Brisbane and Gold Coast as Cyclone Alfred Intensifies
Summary:
Cyclone Alfred is expected to hit the Queensland coastline by early Saturday morning, bringing damaging winds, heavy rainfall, and significant coastal erosion. As a proactive measure, Qantas, Jetstar, and Virgin have suspended flights at Brisbane and Gold Coast airports. The cyclone, categorized as either 1 or 2, has already caused wind speeds up to 98 km/h and has delayed its landfall, prolonging adverse conditions. Significant rainfall has been recorded, prompting concerns about major flooding and property damage, which could cost billions. Authorities have mobilized emergency services and the Australian Defence Force, activated evacuation centers, and distributed sandbags as the cyclone approaches. People living in the affected regions are advised to stay home and avoid travel.
Sources: The Courier-Mail - March 6, 2025
-
 @ da0b9bc3:4e30a4a9
2025-03-06 06:35:31
@ da0b9bc3:4e30a4a9
2025-03-06 06:35:31Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/905374
-
 @ 732c6a62:42003da2
2025-03-06 06:00:53
@ 732c6a62:42003da2
2025-03-06 06:00:53De acordo com a Forbes, a Ripple (Empresa responsável pela Criptomoeda XRP) tem financiado e apoiado campanhas contra a mineração de Bitcoin.
Por que Ripple faz propaganda anti-bitcoin?
Simples: eles são o oposto do Bitcoin em quase tudo. Enquanto o Bitcoin foi criado para ser descentralizado, resistente à censura e independente de instituições, o Ripple é basicamente um serviço bancário 2.0. Eles precisam atacar o Bitcoin para justificar sua própria existência.
O que você não sabe:
- Ripple Labs controla a maioria do XRP: Eles têm um estoque estratégico que pode ser liberado no mercado a qualquer momento. Isso é o oposto de descentralização.
- XRP não é uma moeda para "pessoas comuns": Foi criada para bancos e instituições financeiras. Basicamente, é o "banco central" das criptomoedas.
- Ripple não é blockchain no sentido tradicional: Eles usam um protocolo chamado Ripple Protocol Consensus Algorithm (RPCA), que é mais rápido, mas menos descentralizado.
Os principais ataques do Ripple ao Bitcoin:
- Anti-mineração: O Ripple critica o consumo de energia do Bitcoin, mas esquece que seu próprio sistema depende de servidores centralizados que também consomem energia.
- Anti-reserva estratégica: O Ripple tem um estoque gigante de XRP, mas critica o Bitcoin por ser "deflacionário". Hipocrisia? Nunca ouvi falar.
- Anti-descentralização: O Ripple prega que a descentralização do Bitcoin é "ineficiente", mas o que eles realmente querem é manter o controle nas mãos de poucos.
Análise Psicológica Básica (para você que acha que XRP é o futuro):
- Síndrome do Underdog: Acha que apoiar o Ripple te faz um rebelde, mas na verdade você está torcendo para o sistema bancário tradicional.
- Viés de Confirmação: Só ouve opiniões que validam sua decisão de comprar XRP.
- Efeito Dunning-Kruger: Acha que entender Ripple te torna um especialista em criptomoedas, mas não sabe o que é um hard fork.
Estudo de Caso (Real, mas Você Vai Ignorar):
Carlos, 30 anos, comprou XRP porque "é o futuro das transações bancárias". Ele não sabe que o Ripple está sendo processado pela SEC por vender XRP como um título não registrado. Carlos agora está esperando o "pump" que nunca vem.Conclusão: ou, "volte para a aula de economia do ensino médio"
Ripple não é o futuro das finanças. É só mais um player tentando lucrar em um mercado competitivo. E sua propaganda anti-Bitcoin? Essa só prova que a descentralização assusta quem quer controle. Agora vá estudar blockchain básico — ou pelo menos pare de compartilhar memes com erros de português.
-
 @ 732c6a62:42003da2
2025-03-06 04:33:48
@ 732c6a62:42003da2
2025-03-06 04:33:48De ''Dialética do Oprimido'' a ''Like do Oprimido'': A Queda Livre do Debate que Nunca Existiu.
A moda do momento
Fiquei aproximadamente 8 meses sem ter acesso a nenhum dispositivo. Quando consegui novamente o acesso ao smartphone, percebi algo diferente no debate político brasileiro: enquanto a direita estava se engajando em incontáveis números de curtidas e compartilhamentos com memes que demonstravam críticas ao governo e aos seus ainda poucos apoiadores que se humilham para defender o indefensável, a esquerda radical repetia sua imposição intelectual em comentários de vários posts, incluindo textos, vídeos e tweets com frases semelhantes a "vai ler um livro de história" "nunca leu um livro", "eu estou do lado certo da história" e "se eu fosse irracional eu seria de direita". Tudo isso pra tentar passar uma mensagem de que a história é de esquerda. A tese é: será que eles realmente são tão inteligentes como juram?
Fatos que ignoram enquanto cospem jargões do "lado certo da história":
1. A esquerda também tem seus terraplanistas: Anti-vaxxers de organicafé, terraplanistas do gênero, e os que acham que a Coreia do Norte é uma democracia.
2. Viés de confirmação não é monopólio da direita: Eles compartilham estudos "científicos" do Medium como se fossem peer-reviewed, mas desdenham de dados que contradizem sua narrativa.
3. A direita não é um monolito: Tem desde ancaps que calculam até a última casa decimal até bolsominions que acham que a Terra é plana. Generalizar é... bem, irracional.Estudo de Caso (Fictício, mas Verdadeiro):
Larissa, 23 anos, posta sobre "ciência e razão" enquanto defende horóscopo como "ferramenta de autoconhecimento". Acredita que o capitalismo causa depressão, mas não sabe o que é taxa Selic. Larissa é você após três caipirinhas.A Imposição intelectual que ninguém pediu (mas todos recebem de graça)
A esquerda brasileira, em sua cruzada épica para salvar o mundo dos "fascistas que ousam discordar", adotou uma nova estratégia: transformar complexidade política em slogans de camiseta de feira. A frase "se eu fosse irracional, seria de direita" não é original — é plágio descarado da cartilha do Complexo de Deus em Oferta no AliExpress.
O Quebra-Cabeça da superioridade Auto-Delirante
A tese esquerdista se sustenta em três pilares frágeis:
1. A falácia do "lado certo da história": Como se história fosse um jogo de futebol com narração do João Cléber.
2. A ilusão de que citar Foucault = ter QI elevado: Spoiler: decorar "biopoder" não te torna imune a acreditar em astrologia.
3. A crença de que volume de texto = profundidade: 15 parágrafos no Twitter não equivalem a um semestre de Ciência Política.Dado Cruel: Um estudo da Universidade de Cambridge (2022) mostrou que extremistas de ambos os lados cometem erros lógicos similares. A diferença? A esquerda usa palavras mais bonitas para mascarar a burrice.
A hipocrisia do "nunca tocou em um livro" (enquanto compartilham resumo de livro no TikTok)
A acusação preferida — "você não lê!" — esconde uma ironia deliciosa:
- 72% dos "intelectuais de rede social" citam livros que nunca leram além do título (Fonte: Pesquisa Informal do Twitter, 2023).
- Obras citadas como troféu: "1984" (para chamar Bolsonaro de Big Brother), "O Capital" (para justificar o NFT da Gal Gadot), e "Feminismo para os 99%" (para atacar homens heterossexuais que usam sandália de dedo).Pergunta Incômoda: Se ler Marx fosse garantia de racionalidade, por que a União Soviética acabou em pizza (literalmente, considerando a economia deles)?
Quando a autoimagem colide com a realidade (Ou: por que nenhum esquerdista lassa no teste de turing da coerência)
A esquerda adora se pintar como a Última Trincheira da Razão, mas pratica o que critica:
- Exemplo 1: Defendem "ciência" quando convém (vacinas), mas abraçam pseudociência quando é trendy (cristais energéticos contra o capitalismo).
- Exemplo 2: Chamam a direita de "terraplanista", mas acham que inflação se resolve com tabelamento estatal — a versão econômica de "a Terra é sustentada por tartarugas".
- Exemplo 3: Criticam "fake news", mas compartilham teorias de que o agro "envenena a comida" (enquanto comem sushi de supermercado).Frase-Chave: "Racionalidade seletiva é o novo analfabetismo funcional."
Pergunta Final: Se a esquerda é tão racional, por que não usa a "lógica implacável" para resolver algo além do enquadro perfeito de stories no Instagram?
Enfim
O debate "esquerda racional vs. direita irracional" é só mais um episódio da novela "Brasil: O País que Confunde Opinião com Ataque de Ego". Enquanto uns brincam de "quem tem o QI mais alto", o país queima — literalmente, considerando o Pantanal. Talvez a verdadeira irracionalidade seja gastar energia discutindo superioridade moral enquanto o Wi-Fi cai pela décima vez no dia. Racionalidade não tem lado político. Arrogância, por outro lado, é universal. Sua necessidade de se sentir superior só prova que a lacração é o último refúgio dos fracos de argumento. Agora deviam estudar economia básica — ou pelo menos que parem de achar que "Ah, mas o capitalismo!" é um contra-argumento.
Saudade da época em que a esquerda não se fingia de intelectual.
-
 @ a63655ce:05240c71
2025-03-06 00:48:46
@ a63655ce:05240c71
2025-03-06 00:48:46looks really clean.
window.nostrasked for the key multiple times for some reason -
 @ 6e0ea5d6:0327f353
2025-03-06 00:18:09
@ 6e0ea5d6:0327f353
2025-03-06 00:18:09Ascolta, amico mio...
There come moments when a grown man looks in the mirror and fails to recognize himself.
Naturally, when this happens, there is nothing more fitting than lighting a cigarette, pouring a glass of fine wine, and toasting to oneself—the birth of a new man, forged in the womb of a harsh and sobering reality.
One cannot scatter thorns along a path walked barefoot, nor allow the tongue to speak what the mind may later pay for—but this, we learn only through years of suffering.
Only now do I realize that, among all the teachers I have had, experience was the harshest of them all, for it first administered the test and only afterward taught me the lesson.
In peaceful moments, one can reflect more easily on the world around him. Imagine, then, the depths of reflection that can be reached in a state of true inner tranquility.
If you have never gazed upon the horizon, taken in all the fortune before your eyes, and declared to yourself, "I will own all of this!", then you have never possessed true ambition. However, blind ambition will leave you waking up hungry for wealth and power but going to sleep with an empty soul.
Walk always with honor, pride, and loyalty—let these principles never depart from you nor fail to steady your steps. In your battles, do not wish for your enemies to be handed to you on their knees; instead, seek to gain the strength and ruthlessness to bring them down while they stand.
Your greatest dilemma is the eternal paradox in the life of a businessman within the sacred Sicilian organization: how to acquire power and wealth without placing both feet in hell?
Be careful not to surrender to arrogance. The man who shouts his virtues to the wind will, when he falls, hear only the echo of his own pride.
Let your greatest legacy be to live in a way that does not shame your mother and makes your father proud.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ b8851a06:9b120ba1
2025-03-05 23:03:00
@ b8851a06:9b120ba1
2025-03-05 23:03:00The U.S. isn't just blocking Gaza's reconstruction—it's ensuring Palestinians have no future there.
This week, Washington rejected the Arab League's $53 billion plan to rebuild Gaza. Not because it was unworkable, but because it was unwanted. #Gaza, they say, is "uninhabitable." The solution? Depopulation, disguised as development.
The Riviera Plan: Rebuilding Without Its People
National Security Council spokesman Brian Hughes put it bluntly:
"Gaza is uninhabitable."
This isn't a call for humanitarian intervention. It's a pretext for forced displacement.
Trump's vision transforms Gaza into a "Riviera of the #MiddleEast"—after its population has been relocated. Officials have explicitly stated Palestinians "would not be allowed to return" once reconstruction begins. This isn't rebuilding; it's replacement.
Regional Consensus Rejected
The Arab League's proposal represented rare unity among regional powers. It offered a detailed roadmap for reconstruction while allowing #Palestinians to remain in their homeland.
By dismissing this plan, Washington sent a clear message: Palestinian self-determination remains subordinate to Western geopolitical interests.
This isn't new. For over a century, Western capitals have determined Palestinian futures while treating their voices as irrelevant.
The Fiat War Machine Connection
War and fiat money go hand in hand. Governments don't fund wars through taxes anymore—it's all printed money. Inflation steals from the public silently, financing endless destruction abroad while citizens struggle at home.
As Saifedean Ammous writes in The Fiat Standard: nostr:npub1gdu7w6l6w65qhrdeaf6eyywepwe7v7ezqtugsrxy7hl7ypjsvxksd76nak
"Central banks are essentially war machines, enabling governments to finance endless conflicts through inflation rather than direct taxation."
This system divorces "economic reward from economic productivity, and instead bases it on political allegiance." The result? A world "perpetually lurching from one crisis to another, with devastating consequences for humanity."
Ukraine Parallels: When Support Is Conditional
The U.S. has now halted military aid to #Ukraine, suspending over $1 billion in arms. #Europe scrambles to fill the gap, suddenly realizing the conditional nature of American protection.
Both conflicts reveal the same truth: geopolitical support is increasingly transactional rather than values-based.
As Henry Kissinger observed: "It may be dangerous to be America's enemy, but being America's friend can be fatal."
The Cycle Continues
The U.S. model is simple: fund destruction, control reconstruction, keep the cycle going.
Fiat money makes it possible. Indifference makes it permanent. And yes #Bitcoin can fix it. But will it?
How long before people wake up #nostr? How long before the cycle breaks?
"Fiat money is a tool for governments to control their citizens" as Saifedean rightly says—and now, through endless war, to control the world.
-
 @ f3873798:24b3f2f3
2025-03-05 23:01:12
@ f3873798:24b3f2f3
2025-03-05 23:01:12O café faz parte da rotina de milhões de pessoas, seja para despertar pela manhã, acompanhar uma boa conversa ou até impulsionar a produtividade no trabalho. Mas você já parou para pensar na qualidade do café que consome diariamente? Neste artigo, vamos falar sobre os benefícios do café e as diferenças entre o café extraforte e o café especial.
☕ Benefícios do Café no Dia a Dia

O café não é apenas uma bebida saborosa, mas também oferece diversos benefícios para a saúde, como:
Aumento da energia e concentração – A cafeína estimula o sistema nervoso central, ajudando na atenção e no foco.
Melhora do humor – O consumo moderado de café pode estimular a produção de dopamina, contribuindo para uma sensação de bem-estar.
Propriedades antioxidantes – O café é rico em compostos que combatem os radicais livres, ajudando a prevenir o envelhecimento precoce.
Auxílio na digestão – Para muitas pessoas, o café funciona como um leve estimulante do sistema digestivo.
☕ Café Extraforte vs. Café Especial: Qual a Diferença?

Na prateleira do supermercado ou na cafeteria, há uma grande variedade de cafés. Mas, afinal, qual é a diferença entre o café extraforte e o café especial?
☕Café Extraforte
Produzido a partir de grãos de qualidade inferior, muitas vezes misturados com impurezas.
Possui torra muito escura, o que pode mascarar defeitos do grão.
Tem um sabor mais amargo e intenso, muitas vezes com notas queimadas.
Pode ser mais ácido e difícil de digerir para algumas pessoas.
☕Café Especial
Feito com grãos selecionados e de alta qualidade, sem defeitos.
A torra é mais equilibrada, preservando os aromas e sabores naturais.
Possui notas sensoriais diferenciadas (frutadas, achocolatadas, florais, etc.).
Mais suave e menos ácido, proporcionando uma experiência mais agradável ao paladar.
☕ Qual Escolher para o Dia a Dia?

Se você busca praticidade e um café forte, o extraforte pode ser uma opção. No entanto, se quiser aproveitar melhor os benefícios do café e sentir sabores mais ricos, vale a pena investir no café especial. Além disso, moer os grãos na hora e preparar a bebida com métodos como coador de pano, prensa francesa ou Hario V60 pode transformar sua experiência com o café.
-
 @ b7b1382e:74635e6c
2025-03-05 22:32:18
@ b7b1382e:74635e6c
2025-03-05 22:32:18Abstract
By Lamar Wilson
This white paper examines an alternative taxation framework characterized by three primary components: a uniform 15% flat tax on income, a redistribution mechanism, and a tiered consumption tax structure. The proposed model aims to stimulate economic growth while maintaining social equity through strategic fiscal policy interventions. This paper analyzes the theoretical underpinnings of this approach, its potential macroeconomic implications, distributional effects across income strata, and implementation challenges. The analysis suggests that while the proposed framework offers significant advantages in terms of simplicity and growth incentives, careful consideration must be given to revenue adequacy, wealth concentration effects, and long-term economic sustainability.
1. Introduction
Taxation systems fundamentally shape economic incentive structures, income distribution, and government fiscal capacity. Contemporary tax regimes often reflect accumulated historical policy decisions rather than coherent economic theory, resulting in complex systems with varying degrees of progressivity, efficiency, and equity (Mirrlees et al., 2011). This paper examines a potential alternative taxation framework built upon three pillars: a uniform flat tax, redistribution mechanisms, and stratified consumption taxation.
The theoretical foundation of this approach draws upon both supply-side economics, which emphasizes the importance of investment incentives, and demand-side considerations, which recognize the economic significance of broad-based consumption. By synthesizing these perspectives, the proposed framework attempts to create a self-reinforcing economic cycle wherein simplified taxation stimulates both investment and consumption.
2. Structural Components of the Proposed Framework
2.1 Uniform Flat Income Taxation
The cornerstone of the proposed system is a uniform 15% tax rate applied to income. This component includes two key elements:
-
Individual Taxation: A 15% flat tax applied to gross income across all individual taxpayers, regardless of income level. This approach eliminates tax brackets, deductions, and exemptions that characterize progressive taxation systems.
-
Business Taxation: A parallel 15% flat tax on net business income (profits), allowing for business expense deductions while maintaining a uniform rate across business entities regardless of size, industry, or organizational structure.
The flat tax component represents a significant departure from graduated or progressive taxation systems prevalent in many developed economies. This simplification potentially reduces compliance costs, eliminates bracket-based behavioral distortions, and creates uniform incentive structures across income levels (Hall & Rabushka, 2007).
2.2 Universal Redistribution Mechanism
The second component involves the pooling and redistribution of tax revenue:
-
Collection Aggregation: All tax revenues from both individual and business taxation are consolidated into a unified fiscal pool.
-
Equal Per Capita Distribution: The aggregated tax revenue is redistributed on an equal per capita basis to all individuals within the jurisdiction, functioning as a universal basic income mechanism.
This redistribution mechanism effectively creates a de facto progressive element within the overtly flat system, as redistribution amounts represent a larger percentage of total income for lower-income individuals compared to higher-income individuals (Van Parijs & Vanderborght, 2017).
2.3 Tiered Consumption Taxation
The third component introduces a differentiated consumption tax structure:
-
Essential Goods and Services: A minimal 2% consumption tax applied to essential items including food, healthcare, housing, and utilities.
-
Non-Essential and Luxury Items: A higher consumption tax rate (suggested at 5% or greater) applied to discretionary purchases and luxury goods.
This differentiated approach to consumption taxation acknowledges consumption patterns that vary across income levels, with lower-income households typically allocating a greater proportion of spending to essential goods (Lustig, 2018).
3. Economic Implications Analysis
3.1 Distributive Effects Across Income Levels
3.1.1 Lower-Income Households
The model's impact on lower-income households involves several counterbalancing forces:
- The 15% flat income tax represents a potentially higher nominal rate than many lower-income households currently face under progressive systems.
- The universal redistribution component serves as a direct income supplement, with the amount received likely exceeding tax contributions for this demographic.
- The 2% consumption tax on essentials introduces a modest additional cost on necessary expenditures.
Net analysis suggests that lower-income households would likely experience a positive fiscal impact through this system, as the redistributive component would exceed their combined income and consumption tax obligations (Piketty & Saez, 2013).
3.1.2 Higher-Income Households
For higher-income households, the framework produces different effects:
- The 15% flat income tax rate typically represents a reduction from current progressive tax rates applied to higher income brackets.
- The universal redistribution amount constitutes a proportionally smaller income supplement relative to total income.
- Higher consumption taxes on luxury goods create a de facto progressive element based on discretionary spending patterns.
The net impact on higher-income households would likely be a reduced overall tax burden compared to progressive systems, potentially increasing capital availability for investment (Auerbach & Hassett, 2015).
3.2 Macroeconomic Implications
3.2.1 Investment and Growth Effects
The framework's reduced taxation on higher incomes and business profits theoretically increases capital availability for investment. This aligns with supply-side economic theories suggesting that lower marginal tax rates stimulate economic expansion through:
- Increased business formation and expansion
- Enhanced capital investment
- Improved labor productivity through capital deepening
- Potential innovation stimulation through retained earnings
Empirical research on flat tax implementations in various jurisdictions provides mixed evidence regarding growth effects, with contextual factors playing significant roles in outcomes (Keen et al., 2008).
3.2.2 Demand Stability and Consumption Patterns
The redistribution component creates a consumption floor that may enhance economic stability through:
- Maintaining baseline consumer demand during economic downturns
- Reducing consumption volatility across business cycles
- Supporting broader-based consumption patterns
- Creating demand-side support for business expansion
This mechanism acknowledges the economic significance of broad-based consumption capacity alongside investment incentives (Stiglitz, 2012).
3.2.3 Labor Market Dynamics
The simplified tax structure potentially influences labor market participation through:
- Elimination of high marginal tax rates that may discourage additional work
- Reduced tax-related work disincentives at lower income levels
- Possible increased labor force participation due to simplified income-benefit calculations
- Potential wage effects as businesses retain higher post-tax profits
The framework's impact on labor markets would likely vary across skill levels, industries, and existing labor market institutions (Card & Krueger, 2015).
4. Implementation Challenges and Considerations
4.1 Fiscal Revenue Adequacy
A primary challenge involves ensuring sufficient government revenue, particularly during the transition period:
- The overall tax burden reduction (estimated at approximately 50% compared to current systems) creates potential revenue shortfalls.
- Government spending obligations would require adjustment, postponement, or alternative funding mechanisms.
- Transitional provisions may be necessary to align revenue reductions with spending adaptations.
Potential solutions include phased implementation, temporary supplementary revenue sources, or deliberate acceleration of economic growth to expand the tax base (Auerbach, 2006).
4.2 Wealth Concentration Effects
Despite redistribution mechanisms, the framework may influence wealth concentration dynamics:
- Reduced taxation on higher incomes could accelerate capital accumulation among wealthy individuals.
- Business owners might experience wealth growth exceeding redistribution effects.
- Global investment patterns could divert economic benefits outside the domestic economy.
Addressing these concerns might require calibration of the redistribution component or implementing complementary policies addressing wealth concentration (Piketty, 2014).
4.3 Long-Term Sustainability Considerations
The framework's long-term viability depends on several factors:
- Sustained economic growth sufficient to support government functions with reduced tax rates
- Continued business investment in productive domestic activities rather than financial engineering
- Maintenance of investment-consumption balance to prevent boom-bust cycles
- Evolution of the system in response to changing economic conditions
Supplementary policies supporting research and development, entrepreneurship, and domestic investment may be necessary to ensure the system's sustainability (Acemoglu & Robinson, 2012).
5. Comparative Cost-Benefit Analysis: Proposed System vs. Current Tax Structure
5.1 Compliance Cost Reduction
The current U.S. tax system imposes substantial compliance costs on individuals and businesses that extend far beyond direct tax payments:
- Americans spend approximately 6.5 billion hours annually on tax compliance activities (Taxpayer Advocate Service, 2022)
- The monetary value of compliance time is estimated at $200-400 billion annually (Laffer et al., 2018)
- Businesses spend an estimated $147 billion annually on tax compliance (Tax Foundation, 2021)
- The Internal Revenue Service budget exceeds $13 billion annually for tax administration and enforcement
The proposed flat tax system would dramatically reduce these costs through:
- Elimination of complex deduction and credit calculations (estimated 90% reduction in form complexity)
- Removal of recordkeeping requirements for numerous tax provisions
- Significant reduction in tax planning expenses for both individuals and businesses
- Decreased need for professional tax preparation services
- Streamlined tax enforcement with fewer provisions to interpret and audit
Quantitative analysis suggests that transitioning to the proposed system could reduce overall compliance costs by approximately 70-80%, representing annual savings of $140-320 billion to the U.S. economy (Greenberg, 2020).
5.2 Administrative Efficiency Gains
The current tax administration infrastructure incurs substantial costs:
- The IRS employs approximately 75,000 full-time equivalent positions
- Tax litigation consumes significant judicial resources across multiple court systems
- Regulatory development and guidance require extensive government resources
- Tax enforcement costs represent approximately 35 cents per $100 collected
The proposed system would generate administrative efficiencies through:
- Simplified verification processes requiring fewer personnel
- Reduced need for specialized tax rulings and interpretations
- Lower audit costs due to straightforward compliance requirements
- Streamlined distribution mechanisms leveraging existing payment systems
Conservative estimates suggest administrative cost reductions of 50-60%, representing billions in government savings that could be redirected to essential services or deficit reduction.
5.3 Economic Efficiency Improvements
Beyond direct compliance and administrative costs, the current system creates significant economic distortions:
- Taxpayers make economic decisions influenced by tax considerations rather than underlying economic value
- Complex provisions create market inefficiencies and misallocation of resources
- High marginal rates discourage additional productive activity
- International tax complexities influence global investment decisions
The proposed system addresses these inefficiencies through:
- Uniform treatment of income regardless of source
- Elimination of tax-motivated transaction structures
- Reduced incentives for artificial entity structures
- Simplified international transactions with domestic reinvestment incentives
Economic models suggest these efficiency improvements could increase GDP by 0.5-1.0% annually beyond direct compliance savings (Jorgenson & Yun, 2012).
5.4 Distributional Cost Analysis
The current system's compliance burden falls disproportionately across income levels:
- Lower-income taxpayers spend a higher percentage of their income on tax compliance
- Small businesses face compliance costs estimated at $1,500-$4,000 per employee
- Middle-income taxpayers navigate complex provisions with limited professional assistance
- High-income taxpayers allocate substantial resources to tax planning and compliance
The proposed system redistributes this burden by:
- Equalizing compliance requirements across income levels
- Substantially reducing small business administrative overhead
- Eliminating the need for complex tax planning strategies
- Providing transparent, predictable tax consequences for economic decisions
This redistribution of compliance costs represents an additional progressive element beyond the direct redistribution component, with estimated financial benefits to lower and middle-income households of $300-500 annually in reduced compliance costs.
6. Conclusion
The proposed tripartite taxation framework offers a conceptually coherent alternative to conventional progressive taxation systems. By combining flat income taxation with universal redistribution and differentiated consumption taxes, the approach attempts to simultaneously address supply-side investment incentives and demand-side consumption support.
The theoretical analysis suggests potential advantages in terms of simplicity, economic growth stimulation, and maintenance of social safety net functions. However, significant implementation challenges exist regarding revenue adequacy, wealth concentration effects, and long-term economic sustainability.
Further empirical research, potentially through regional pilot implementations or microsimulation modeling, would enhance understanding of the practical implications of this taxation approach. While the framework presents a promising theoretical model, its successful implementation would require careful calibration to specific economic contexts, thoughtful transition planning, and ongoing adjustment based on observed outcomes.
References
Acemoglu, D., & Robinson, J. A. (2012). Why nations fail: The origins of power, prosperity, and poverty. Crown Business.
Greenberg, S. (2020). Reforming the U.S. tax system: Evidence on economic growth and distribution. American Enterprise Institute.
Jorgenson, D. W., & Yun, K. Y. (2012). Tax reform and the cost of capital. Oxford University Press.
Laffer, A. B., Moore, S., & Williams, J. (2018). The wealth of states: How taxes, energy, and worker freedom change everything. Wiley.
Tax Foundation (2021). The cost of tax compliance. Fiscal Fact No. 512.
Taxpayer Advocate Service (2022). Annual report to Congress. Internal Revenue Service.
Auerbach, A. J. (2006). The choice between income and consumption taxes: A primer. NBER Working Paper Series.
Auerbach, A. J., & Hassett, K. (2015). Capital taxation in the twenty-first century. American Economic Review, 105(5), 38-42.
Card, D., & Krueger, A. B. (2015). Myth and measurement: The new economics of the minimum wage. Princeton University Press.
Hall, R. E., & Rabushka, A. (2007). The flat tax. Hoover Institution Press.
Keen, M., Kim, Y., & Varsano, R. (2008). The "flat tax(es)": Principles and experience. International Tax and Public Finance, 15(6), 712-751.
Lustig, N. (2018). Fiscal policy, income redistribution and poverty reduction in low and middle income countries. Commitment to Equity Handbook.
Mirrlees, J., Adam, S., Besley, T., Blundell, R., Bond, S., Chote, R., Gammie, M., Johnson, P., Myles, G., & Poterba, J. (2011). Tax by design. Oxford University Press.
Piketty, T. (2014). Capital in the twenty-first century. Harvard University Press.
Piketty, T., & Saez, E. (2013). Optimal labor income taxation. Handbook of Public Economics, 5, 391-474.
Stiglitz, J. E. (2012). The price of inequality: How today's divided society endangers our future. W.W. Norton & Company.
Van Parijs, P., & Vanderborght, Y. (2017). Basic income: A radical proposal for a free society and a sane economy. Harvard University Press.
A Tripartite Approach to Fiscal Reform: Analyzing the Economic Impact of a Flat Tax, Redistribution, and Consumption Tax Framework
Author: Lamar Wilson
Abstract
By Lamar Wilson
This white paper examines an alternative taxation framework characterized by three primary components: a uniform 15% flat tax on income, a redistribution mechanism, and a tiered consumption tax structure. The proposed model aims to stimulate economic growth while maintaining social equity through strategic fiscal policy interventions. This paper analyzes the theoretical underpinnings of this approach, its potential macroeconomic implications, distributional effects across income strata, and implementation challenges. The analysis suggests that while the proposed framework offers significant advantages in terms of simplicity and growth incentives, careful consideration must be given to revenue adequacy, wealth concentration effects, and long-term economic sustainability.
1. Introduction
Taxation systems fundamentally shape economic incentive structures, income distribution, and government fiscal capacity. Contemporary tax regimes often reflect accumulated historical policy decisions rather than coherent economic theory, resulting in complex systems with varying degrees of progressivity, efficiency, and equity (Mirrlees et al., 2011). This paper examines a potential alternative taxation framework built upon three pillars: a uniform flat tax, redistribution mechanisms, and stratified consumption taxation.
The theoretical foundation of this approach draws upon both supply-side economics, which emphasizes the importance of investment incentives, and demand-side considerations, which recognize the economic significance of broad-based consumption. By synthesizing these perspectives, the proposed framework attempts to create a self-reinforcing economic cycle wherein simplified taxation stimulates both investment and consumption.
2. Structural Components of the Proposed Framework
2.1 Uniform Flat Income Taxation
The cornerstone of the proposed system is a uniform 15% tax rate applied to income. This component includes two key elements:
-
Individual Taxation: A 15% flat tax applied to gross income across all individual taxpayers, regardless of income level. This approach eliminates tax brackets, deductions, and exemptions that characterize progressive taxation systems.
-
Business Taxation: A parallel 15% flat tax on net business income (profits), allowing for business expense deductions while maintaining a uniform rate across business entities regardless of size, industry, or organizational structure.
The flat tax component represents a significant departure from graduated or progressive taxation systems prevalent in many developed economies. This simplification potentially reduces compliance costs, eliminates bracket-based behavioral distortions, and creates uniform incentive structures across income levels (Hall & Rabushka, 2007).
2.2 Universal Redistribution Mechanism
The second component involves the pooling and redistribution of tax revenue:
-
Collection Aggregation: All tax revenues from both individual and business taxation are consolidated into a unified fiscal pool.
-
Equal Per Capita Distribution: The aggregated tax revenue is redistributed on an equal per capita basis to all individuals within the jurisdiction, functioning as a universal basic income mechanism.
This redistribution mechanism effectively creates a de facto progressive element within the overtly flat system, as redistribution amounts represent a larger percentage of total income for lower-income individuals compared to higher-income individuals (Van Parijs & Vanderborght, 2017).
2.3 Tiered Consumption Taxation
The third component introduces a differentiated consumption tax structure:
-
Essential Goods and Services: A minimal 2% consumption tax applied to essential items including food, healthcare, housing, and utilities.
-
Non-Essential and Luxury Items: A higher consumption tax rate (suggested at 5% or greater) applied to discretionary purchases and luxury goods.
This differentiated approach to consumption taxation acknowledges consumption patterns that vary across income levels, with lower-income households typically allocating a greater proportion of spending to essential goods (Lustig, 2018).
3. Economic Implications Analysis
3.1 Distributive Effects Across Income Levels
3.1.1 Lower-Income Households
The model's impact on lower-income households involves several counterbalancing forces:
- The 15% flat income tax represents a potentially higher nominal rate than many lower-income households currently face under progressive systems.
- The universal redistribution component serves as a direct income supplement, with the amount received likely exceeding tax contributions for this demographic.
- The 2% consumption tax on essentials introduces a modest additional cost on necessary expenditures.
Net analysis suggests that lower-income households would likely experience a positive fiscal impact through this system, as the redistributive component would exceed their combined income and consumption tax obligations (Piketty & Saez, 2013).
3.1.2 Higher-Income Households
For higher-income households, the framework produces different effects:
- The 15% flat income tax rate typically represents a reduction from current progressive tax rates applied to higher income brackets.
- The universal redistribution amount constitutes a proportionally smaller income supplement relative to total income.
- Higher consumption taxes on luxury goods create a de facto progressive element based on discretionary spending patterns.
The net impact on higher-income households would likely be a reduced overall tax burden compared to progressive systems, potentially increasing capital availability for investment (Auerbach & Hassett, 2015).
3.2 Macroeconomic Implications
3.2.1 Investment and Growth Effects
The framework's reduced taxation on higher incomes and business profits theoretically increases capital availability for investment. This aligns with supply-side economic theories suggesting that lower marginal tax rates stimulate economic expansion through:
- Increased business formation and expansion
- Enhanced capital investment
- Improved labor productivity through capital deepening
- Potential innovation stimulation through retained earnings
Empirical research on flat tax implementations in various jurisdictions provides mixed evidence regarding growth effects, with contextual factors playing significant roles in outcomes (Keen et al., 2008).
3.2.2 Demand Stability and Consumption Patterns
The redistribution component creates a consumption floor that may enhance economic stability through:
- Maintaining baseline consumer demand during economic downturns
- Reducing consumption volatility across business cycles
- Supporting broader-based consumption patterns
- Creating demand-side support for business expansion
This mechanism acknowledges the economic significance of broad-based consumption capacity alongside investment incentives (Stiglitz, 2012).
3.2.3 Labor Market Dynamics
The simplified tax structure potentially influences labor market participation through:
- Elimination of high marginal tax rates that may discourage additional work
- Reduced tax-related work disincentives at lower income levels
- Possible increased labor force participation due to simplified income-benefit calculations
- Potential wage effects as businesses retain higher post-tax profits
The framework's impact on labor markets would likely vary across skill levels, industries, and existing labor market institutions (Card & Krueger, 2015).
4. Implementation Challenges and Considerations
4.1 Fiscal Revenue Adequacy
A primary challenge involves ensuring sufficient government revenue, particularly during the transition period:
- The overall tax burden reduction (estimated at approximately 50% compared to current systems) creates potential revenue shortfalls.
- Government spending obligations would require adjustment, postponement, or alternative funding mechanisms.
- Transitional provisions may be necessary to align revenue reductions with spending adaptations.
Potential solutions include phased implementation, temporary supplementary revenue sources, or deliberate acceleration of economic growth to expand the tax base (Auerbach, 2006).
4.2 Wealth Concentration Effects
Despite redistribution mechanisms, the framework may influence wealth concentration dynamics:
- Reduced taxation on higher incomes could accelerate capital accumulation among wealthy individuals.
- Business owners might experience wealth growth exceeding redistribution effects.
- Global investment patterns could divert economic benefits outside the domestic economy.
Addressing these concerns might require calibration of the redistribution component or implementing complementary policies addressing wealth concentration (Piketty, 2014).
4.3 Long-Term Sustainability Considerations
The framework's long-term viability depends on several factors:
- Sustained economic growth sufficient to support government functions with reduced tax rates
- Continued business investment in productive domestic activities rather than financial engineering
- Maintenance of investment-consumption balance to prevent boom-bust cycles
- Evolution of the system in response to changing economic conditions
Supplementary policies supporting research and development, entrepreneurship, and domestic investment may be necessary to ensure the system's sustainability (Acemoglu & Robinson, 2012).
5. Comparative Cost-Benefit Analysis: Proposed System vs. Current Tax Structure
5.1 Compliance Cost Reduction
The current U.S. tax system imposes substantial compliance costs on individuals and businesses that extend far beyond direct tax payments:
- Americans spend approximately 6.5 billion hours annually on tax compliance activities (Taxpayer Advocate Service, 2022)
- The monetary value of compliance time is estimated at $200-400 billion annually (Laffer et al., 2018)
- Businesses spend an estimated $147 billion annually on tax compliance (Tax Foundation, 2021)
- The Internal Revenue Service budget exceeds $13 billion annually for tax administration and enforcement
The proposed flat tax system would dramatically reduce these costs through:
- Elimination of complex deduction and credit calculations (estimated 90% reduction in form complexity)
- Removal of recordkeeping requirements for numerous tax provisions
- Significant reduction in tax planning expenses for both individuals and businesses
- Decreased need for professional tax preparation services
- Streamlined tax enforcement with fewer provisions to interpret and audit
Quantitative analysis suggests that transitioning to the proposed system could reduce overall compliance costs by approximately 70-80%, representing annual savings of $140-320 billion to the U.S. economy (Greenberg, 2020).
5.2 Administrative Efficiency Gains
The current tax administration infrastructure incurs substantial costs:
- The IRS employs approximately 75,000 full-time equivalent positions
- Tax litigation consumes significant judicial resources across multiple court systems
- Regulatory development and guidance require extensive government resources
- Tax enforcement costs represent approximately 35 cents per $100 collected
The proposed system would generate administrative efficiencies through:
- Simplified verification processes requiring fewer personnel
- Reduced need for specialized tax rulings and interpretations
- Lower audit costs due to straightforward compliance requirements
- Streamlined distribution mechanisms leveraging existing payment systems
Conservative estimates suggest administrative cost reductions of 50-60%, representing billions in government savings that could be redirected to essential services or deficit reduction.
5.3 Economic Efficiency Improvements
Beyond direct compliance and administrative costs, the current system creates significant economic distortions:
- Taxpayers make economic decisions influenced by tax considerations rather than underlying economic value
- Complex provisions create market inefficiencies and misallocation of resources
- High marginal rates discourage additional productive activity
- International tax complexities influence global investment decisions
The proposed system addresses these inefficiencies through:
- Uniform treatment of income regardless of source
- Elimination of tax-motivated transaction structures
- Reduced incentives for artificial entity structures
- Simplified international transactions with domestic reinvestment incentives
Economic models suggest these efficiency improvements could increase GDP by 0.5-1.0% annually beyond direct compliance savings (Jorgenson & Yun, 2012).
5.4 Distributional Cost Analysis
The current system's compliance burden falls disproportionately across income levels:
- Lower-income taxpayers spend a higher percentage of their income on tax compliance
- Small businesses face compliance costs estimated at $1,500-$4,000 per employee
- Middle-income taxpayers navigate complex provisions with limited professional assistance
- High-income taxpayers allocate substantial resources to tax planning and compliance
The proposed system redistributes this burden by:
- Equalizing compliance requirements across income levels
- Substantially reducing small business administrative overhead
- Eliminating the need for complex tax planning strategies
- Providing transparent, predictable tax consequences for economic decisions
This redistribution of compliance costs represents an additional progressive element beyond the direct redistribution component, with estimated financial benefits to lower and middle-income households of $300-500 annually in reduced compliance costs.
6. Conclusion
The proposed tripartite taxation framework offers a conceptually coherent alternative to conventional progressive taxation systems. By combining flat income taxation with universal redistribution and differentiated consumption taxes, the approach attempts to simultaneously address supply-side investment incentives and demand-side consumption support.
The theoretical analysis suggests potential advantages in terms of simplicity, economic growth stimulation, and maintenance of social safety net functions. However, significant implementation challenges exist regarding revenue adequacy, wealth concentration effects, and long-term economic sustainability.
Further empirical research, potentially through regional pilot implementations or microsimulation modeling, would enhance understanding of the practical implications of this taxation approach. While the framework presents a promising theoretical model, its successful implementation would require careful calibration to specific economic contexts, thoughtful transition planning, and ongoing adjustment based on observed outcomes.
References
Acemoglu, D., & Robinson, J. A. (2012). Why nations fail: The origins of power, prosperity, and poverty. Crown Business.
Greenberg, S. (2020). Reforming the U.S. tax system: Evidence on economic growth and distribution. American Enterprise Institute.
Jorgenson, D. W., & Yun, K. Y. (2012). Tax reform and the cost of capital. Oxford University Press.
Laffer, A. B., Moore, S., & Williams, J. (2018). The wealth of states: How taxes, energy, and worker freedom change everything. Wiley.
Tax Foundation (2021). The cost of tax compliance. Fiscal Fact No. 512.
Taxpayer Advocate Service (2022). Annual report to Congress. Internal Revenue Service.
Auerbach, A. J. (2006). The choice between income and consumption taxes: A primer. NBER Working Paper Series.
Auerbach, A. J., & Hassett, K. (2015). Capital taxation in the twenty-first century. American Economic Review, 105(5), 38-42.
Card, D., & Krueger, A. B. (2015). Myth and measurement: The new economics of the minimum wage. Princeton University Press.
Hall, R. E., & Rabushka, A. (2007). The flat tax. Hoover Institution Press.
Keen, M., Kim, Y., & Varsano, R. (2008). The "flat tax(es)": Principles and experience. International Tax and Public Finance, 15(6), 712-751.
Lustig, N. (2018). Fiscal policy, income redistribution and poverty reduction in low and middle income countries. Commitment to Equity Handbook.
Mirrlees, J., Adam, S., Besley, T., Blundell, R., Bond, S., Chote, R., Gammie, M., Johnson, P., Myles, G., & Poterba, J. (2011). Tax by design. Oxford University Press.
Piketty, T. (2014). Capital in the twenty-first century. Harvard University Press.
Piketty, T., & Saez, E. (2013). Optimal labor income taxation. Handbook of Public Economics, 5, 391-474.
Stiglitz, J. E. (2012). The price of inequality: How today's divided society endangers our future. W.W. Norton & Company.
Van Parijs, P., & Vanderborght, Y. (2017). Basic income: A radical proposal for a free society and a sane economy. Harvard University Press.
-
-
 @ 6389be64:ef439d32
2025-03-05 21:18:52
@ 6389be64:ef439d32
2025-03-05 21:18:52Carbon is a "Long-Tail" asset: the residual earnings that come from an asset after it has had its initial market impact.
The Carbon Cascade converts labile into recalcitrant carbon.
During transformation power is generated and lands restored.
Total production of biomass per annum is 100 billion tons of carbon and at $500 to $2,000 per ton of biochar that's $100 trillion of potential carbon trading on the open market. (fanciful to be sure)
originally posted at https://stacker.news/items/904996
-
 @ 878dff7c:037d18bc
2025-03-05 20:37:35
@ 878dff7c:037d18bc
2025-03-05 20:37:35Overview
Tropical Cyclone Alfred, currently a Category 2 system, is approaching Australia's eastern coast, with landfall anticipated between the Sunshine Coast and Gold Coast early Friday. This rare event has prompted widespread preparations and warnings across Queensland and New South Wales. Authorities are urging residents in vulnerable areas to evacuate and brace for destructive winds, heavy rainfall, and potential life-threatening flooding. TROPICAL CYCLONE FORECAST TRACK MAP
(Cover photo thanks to our 'unfortunately on the ground' photographer Sean. Stay safe mate!)
Queensland and New South Wales Brace for Cyclone Alfred's Impact
Summary:
Residents in Queensland and northern New South Wales are preparing for Tropical Cyclone Alfred, expected to make landfall early Friday between the Sunshine Coast and Gold Coast. The Category 2 storm is forecasted to bring severe winds and heavy rain, with potential for major flooding. Emergency measures include power outages, flight cancellations, school closures, and activation of emergency centers. The Australian Defence Force has been engaged to assist with response efforts. Sources: The Guardian - 6 March 2025
Authorities Issue Evacuation Warnings Ahead of Cyclone Alfred
Summary:
Australian authorities have issued major evacuation warnings ahead of Tropical Cyclone Alfred's expected landfall on Friday morning. The cyclone, categorized as Category 2, is anticipated to bring winds of 155 km/h and 800 mm of rainfall, potentially leading to dangerous and life-threatening conditions. Areas like Brisbane, the Gold Coast, and Sunshine Coast are in the cyclone's projected path. Residents in flood-prone and coastal areas are urged to evacuate and make necessary preparations, including stocking up on water and non-perishable food. The Australian government has declared a state of emergency and engaged the Australian Defence Force to assist with evacuation and disaster response efforts. Sources: The Sun - 6 March 2025
Residents Prepare for First Cyclone in Over Five Decades
Summary:
Residents in Brisbane and the Gold Coast are preparing for Tropical Cyclone Alfred, the first cyclone in 51 years to hit the Australian east coast near Brisbane. The cyclone is predicted to make landfall late Thursday or early Friday, bringing destructive winds, large swells, and potential life-threatening flooding. Brisbane, with over 3 million residents, may see up to 20,000 homes affected by flooding. The government has provided 250,000 sandbags and established cyclone refuge centers. Schools, public transport, and non-urgent hospital surgeries will be suspended. Queensland Premier David Crisafulli has urged residents to prepare their homes and plan evacuation routes. Sources: AP News - 6 March 2025
Cyclone Alfred's Approach Prompts Widespread Preparations
Summary:
Cyclone Alfred, a Category 2 storm, is approaching the Tweed Coast near Brisbane, expected to make landfall late Thursday or early Friday. As tension mounts, residents are bracing for potential disaster with power outages and water contamination being the main concerns. Supermarkets are emptied of essential supplies, and emergency preparations, such as sandbagging and securing properties, are in full swing. The community displays remarkable solidarity, with neighbors helping one another and sharing real-time updates. Surfers are taking advantage of the monster swells, enjoying the waves despite the looming threat. Families face difficult decisions on whether to stay or evacuate, while prioritizing the safety and well-being of their loved ones. With a keen sense of unity and preparedness, the community waits in hope that their efforts will withstand the upcoming storm. Sources: News.com.au - 6 March 2025
Cyclone Alfred's Unusual Path Raises Concerns
Summary:
Australia is preparing for a rare tropical cyclone, named Alfred, approaching Brisbane. Authorities are urging residents in flood-prone suburbs to evacuate due to potential destructive wind gusts up to 155 kph and significant rainfall that could lead to life-threatening flash flooding. The storm is expected to land as a Category 2 cyclone early on Friday. Evacuation efforts are in place, with heavy-lift helicopters deployed and evacuation centers being opened. Schools and public transport will shut down, and flights have been canceled in the affected regions. This area of southeast Queensland and northern New South Wales has not experienced such a cyclone for over fifty years. Sources: Reuters - 6 March 2025
Ice Cube Shares Experience Amid Cyclone Alfred
Summary:
Ice Cube is currently staying at a beachfront hotel in Australia as Cyclone Alfred intensifies. The 55-year-old rapper and actor, who is there for upcoming performances, humorously commented about experiencing a cyclone for the first time. Residents in flood-prone regions have been advised to evacuate, with heavy rains and strong winds expected to cause potentially life-threatening flash floods and severe storm conditions. The cyclone is particularly significant for Queensland, which hasn't seen such severe weather in decades. Ice Cube also denied rumors of his involvement in an 'Anaconda' reboot being filmed in Australia, stating he was only there for his Sydney show. Sources: People - 6 March 2025
Cyclone Alfred's Impact on Northern New South Wales
Summary:
Residents in Northern New South Wales are preparing for the impacts of Cyclone Alfred, with rainfalls of up to 400 millimeters expected, alongside winds of up to 150 kilometers per hour and likely flooding. The cyclone's approach has led to heightened concerns and preparations in the region. Sources: ABC News - 6 March 2025
Authorities Urge Evacuations as Cyclone Alfred Nears
Summary:
Residents in flood-prone suburbs of Brisbane and the Gold Coast are being urged to evacuate as Cyclone Alfred approaches. The storm is expected to bring destructive winds and heavy rainfall, leading to life-threatening flash flooding. Evacuation centers have been established, and emergency services are on high alert to assist those in need. Sources: The Guardian - 6 March 2025
-
 @ 05933d87:81bac46e
2025-03-05 20:17:49
@ 05933d87:81bac46e
2025-03-05 20:17:49A few months ago, an Uber driver alerted me to the presence of his rival. By that point, Waymo had been testing in Austin for over a year. I hid my excitement during the ride but I applied as a beta tester, noting my belonging to the demographics a PM might test for. My application went ignored until, huzzah, Waymo sent me an email yesterday announcing their self-driving cars are available directly through Uber in Austin.
I configured my allegiance to our new overlords swearing in on my screened sandwich of silicon.
Without willing it, and having forgot my new religion, I woke earlier than planned today and hailed a ride. The app spoke to me, "if you wait 3 minutes longer, we'll send you a car without a driver." For five minutes, I watched a car but not a driver move in the direction of me and my screen.
The ride was nice. I didn't have to theatrically rush to a waiting human. There was less social weirdness than I would normally sit with on a ride. I could inspect the car without risking the driver sense that I'm inspecting them. The car couldn't look at me buffering, deciphering if I am homeless or merely look it. I got to pick my own music. I got to watch people un-contacted by Waymo watch the car.
But ... it drove a lot more like a robot driving a car than a human driving a car. It pumped the brakes a few times as we passed weirdly parked cars uncertain (apparently) if the car might move into our lane. Once it signaled that we were headed into oncoming traffic as a street widened from one lane to two. Worst of all, it dropped me off near an anomalous stretch of sidewalk where my door opened to a wall, and if I were to climb and get out the other side, I'd arrive in the middle lane of a busy street. Trapped, I pinched myself through the door and, like Laura Croft, navigated the road's edge to a sidewalk.
tbh I'm still excited for my next Waymo ride. I'll just choose a different drop-off address.
originally posted at https://stacker.news/items/904830
-
 @ 878dff7c:037d18bc
2025-03-05 20:12:53
@ 878dff7c:037d18bc
2025-03-05 20:12:53Queensland Premier Urges Immediate Preparations Ahead of Cyclone Alfred
Summary:
Queensland Premier David Crisafulli has urged residents to complete their preparations immediately as Tropical Cyclone Alfred approaches. The Category 2 cyclone is expected to bring heavy rainfall, destructive winds, and potential flooding to South-East Queensland and Northern New South Wales. Public transport services and elective surgeries have been canceled, and hundreds of schools will remain closed through the week. Residents are advised to stay indoors and ensure their safety during the cyclone's landfall.
Sources: The Guardian - March 5, 2025, News.com.au - March 6, 2025
Evacuation Orders Issued as Cyclone Alfred Approaches
Summary:
Authorities have issued evacuation orders for residents in Northern New South Wales, particularly in areas from Tweed to Yamba, as Cyclone Alfred intensifies. The cyclone is expected to bring gale-force winds, heavy rainfall up to 400 mm, and significant flooding. Schools and flights have been disrupted, with widespread closures and cancellations in the region. Coastal areas are experiencing high winds and massive waves, increasing the risk of flash floods. Emergency services are on high alert, preparing residents and reinforcing infrastructure to manage imminent threats.
Sources: The Daily Telegraph - March 6, 2025, News.com.au - March 6, 2025
Liberal Senator Alex Antic's Rise Signals Shift to Conservatism in South Australia
Summary:
Liberal Senator Alex Antic has ascended to the top position on South Australia's Senate ticket, marking a significant shift from the state's traditionally moderate Liberal stance to a more conservative direction. This change follows the resignation of veteran moderate Simon Birmingham and an influx of social conservatives and libertarians into the party. Antic, known for his controversial views, believes that conservative values are gaining traction as the world reaches "peak woke." He emphasizes the importance of adhering to traditional conservative principles to appeal to families concerned about social issues and younger individuals focused on economic matters. Despite past conflicts with party moderates, Antic is optimistic about the party's future under leaders like Peter Dutton, noting similar conservative movements globally. Sources: The Australian - March 5, 2025
Government's $130k Weekly Legal Fees for Toll Reform Under Scrutiny
Summary:
The Minns government's efforts to reform Sydney's toll network have cost taxpayers over $8 million, with legal advice alone amounting to $130,000 per week since February 5, 2025. Despite these expenditures, significant changes have yet to be implemented, leading to criticism over the prioritization of consultancy fees over actionable toll reforms.
Sources: The Daily Telegraph - March 6, 2025
Tech Giants Generate $27 Billion Annually from Australian Consumers
Summary:
An analysis by the Parliamentary Budget Office reveals that the top 16 tech companies, including Google, Microsoft, Meta, and Amazon, collectively earn $26.7 billion annually from Australian consumers. The Greens propose a 3% tax on these companies' revenues exceeding $20 million, potentially generating $11.5 billion for the government to fund essential services like dental care in Medicare. However, this proposal faces challenges due to potential retaliatory measures from the U.S. government. Sources: The Guardian - 6 March 2025
Melioidosis Outbreak in Queensland
Summary:
Queensland is experiencing a significant outbreak of melioidosis, a serious disease caused by the bacteria Burkholderia pseudomallei, typically found in soil and freshwater. The bacteria can infect humans and animals through cuts, contaminated water, or inhalation. Symptoms include fever, headache, respiratory issues, and muscle pain. This year, there have been over 90 confirmed cases and 15 deaths in Queensland, higher than usual. The outbreak is believed to be linked to heavy rainfall and flooding, increasing the bacteria's prevalence. Preventative measures include wearing protective gear in wet areas and seeking early medical attention for symptoms like fever and breathing difficulties.
Sources: The Advertiser - 3 March 2025
Philippine Defense Chief Warns Against Chinese Restrictions in South China Sea
Summary:
Philippine Defense Secretary Gilberto Teodoro warned that the Philippines and its allies would respond to any Chinese attempt to impose an air defense zone or restrict flights over the South China Sea. Teodoro highlighted China's growing aggression in the disputed waters, which has led to increased confrontations involving Chinese and Philippine forces, as well as incidents with U.S. and Australian military aircraft. Recent encounters have included close flybys and warning flares from Chinese aircraft. Teodoro emphasized that China's actions pose a major threat to both Philippine and global security due to the region's critical trade routes. He stated that defense officials are preparing contingency measures and could act alone or with international partners to counter potential Chinese aggression. Teodoro noted the possibility of a broader coalition forming to resist China's attempts to reshape international law and norms. Sources: Associated Press - 6 March 2025
Amazon Joins Quantum Computing Race with 'Cat Qubit' Chip
Summary:
Amazon has unveiled its new quantum computing chip, Ocelot, which utilizes "cat qubit" technology to significantly reduce quantum errors—a major hurdle in developing commercially viable quantum systems. This advancement positions Amazon alongside other tech giants like Google and Microsoft in the quest for functional quantum computers.
Sources: SHRM - March 6, 2025
New $1 Billion Fund Launched to Boost Australia's Circular Economy
Summary:
Planet Ark and Boston Global have partnered to launch the BG Planet Ark Circular Future Fund, aiming to raise $1 billion by 2030 to invest in businesses promoting sustainability, reducing carbon emissions, and enhancing the circular economy. This initiative aligns with Australia's Circular Economy Framework, which seeks to double circularity by 2035 and add $26 billion annually to the GDP. Initial funding of $100 million has been secured, targeting sectors like regenerative farming and waste-to-energy solutions.
Sources: The Australian - March 6, 2025
Australia's Foreign Minister Comments on Trump's Second Term
Summary:
Foreign Minister Penny Wong has remarked that Donald Trump's second presidency is already more disruptive than his first. She noted that Australia's government is dealing with a very different American administration, reflecting concerns about potential shifts in international relations and policies affecting Australia's strategic interests.
Sources: Reuters - March 5, 2025
-
 @ 2e8970de:63345c7a
2025-03-05 19:50:10
@ 2e8970de:63345c7a
2025-03-05 19:50:10It leads to fast, and massive weight loss by not just suppressing appetite, but also by upregulating metabolism.
https://www.nejm.org/doi/full/10.1056/NEJMoa2301972
originally posted at https://stacker.news/items/904851
-
 @ 4925ea33:025410d8
2025-03-05 19:44:37
@ 4925ea33:025410d8
2025-03-05 19:44:37De acordo com a Resolução 03/25 do Conselho Federal de Farmácia a Aromaterapia é uma prática terapêutica que utiliza as propriedades dos óleos essenciais para restaurar o equilíbrio e a harmonia do organismo, promovendo a saúde física, mental e emocional. Essa técnica baseia-se no uso dos compostos aromáticos naturais extraídos das plantas para estimular respostas neurológicas e bioquímicas no corpo.
Os óleos essenciais atuam diretamente no sistema límbico, região do cérebro responsável pelas emoções, memórias e comportamentos. Mas seus benefícios vão muito além do bem-estar emocional! Eles possuem propriedades terapêuticas únicas, podendo atuar como cicatrizantes, antifúngicos, antibacterianos, anti-inflamatórios e até auxiliares no alívio de dores e tensões musculares. Além da inalação, os óleos podem ser aplicados topicamente, sendo absorvidos pela pele e interagindo com o organismo de maneira profunda e eficaz.
No entanto, é importante lembrar que os óleos essenciais são altamente concentrados e contêm substâncias que podem causar alergias ou irritações se usados de forma inadequada. Por isso, é essencial buscar orientação de um profissional qualificado para garantir um tratamento seguro e eficaz.
Quer saber como a Aromaterapia pode transformar seu bem-estar? Agende uma consulta comigo e descubra os benefícios personalizados para você.
-
 @ b4403b24:83542d4e
2025-03-05 19:18:39
@ b4403b24:83542d4e
2025-03-05 19:18:39I can't believe so many shitcoiners are invited to attend 🫣
originally posted at https://stacker.news/items/904818
-
 @ a296b972:e5a7a2e8
2025-03-05 18:34:49
@ a296b972:e5a7a2e8
2025-03-05 18:34:49Von Egon Bahr stammt der Satz: „Wir können politisch alles Mögliche ändern, nur nicht die Geografie.“ Er scheint der letzte deutsche Politiker gewesen zu sein, der wusste, dass Europa zwischen den USA im Westen und Russland im Osten liegt. Die tektonische Plattenverschiebung wird daran über kurz oder lang auch nichts ändern.
Europa, besonders Deutschland, wird erneut von der Weltgeschichte die Möglichkeit gegeben, seine ihm ureigenste Rolle anzunehmen, nämlich endlich eine neutrale, vermittelnde Rolle zwischen West und Ost zu ergreifen. Stattdessen verscherzt Europa es sich derzeit mit beiden Weltmächten. Das muss man erst einmal hinbekommen. Wie doof kann man sein? Brücken bauen scheint man in Deutschland nicht mehr zu können. Sieht man ja in Dresden.
Deutschland scheint diese Chance erneut nicht zu erkennen, da es spätestens seit dem C-Ereignis, entgegen den USA zumindest teilweise, bis heute nicht wieder zu Verstand gekommen ist. Eigentlich schon früher, nur da hat man es noch nicht so gemerkt.
Bis auf wenige Ausnahmen wird ganz Europa derzeit von Verrückten und deren Erfüllungsgehilfen geleitet. Allein die Aussage der CDU in Deutschland einen Tag nach der Wahl, „Die Ukraine muss den Krieg gewinnen“, zeigt, dass weiterhin nicht alle Porzellan-Trinkgefäße in dem dafür vorgesehenen Küchenmöbel vorhanden sind.
Es werden „Kriegs-Konferenzen“ einberufen, wie man die Ukraine weiter mit Geld und Waffen unterstützen kann, statt zu erkennen, dass sich der Wind Richtung Frieden gedreht hat. Europa hat zwar nichts zu sagen, dennoch kann Dummheit gefährlich werden. Es können Teller zerdeppert werden, die man besser nicht angerührt hätte.
Jeder Banker schüttelt den Kopf und drückt auf den Alarmknopf unter der Schreibtischplatte, wenn man zu ihm geht und um ein Sondervermögen ansucht. Hexenmeister Deutschland kann Geld herbeizaubern, allein durch seinen politischen Willen, Kraft seiner Gedanken. Schöpfung aus dem Nichts. Und warum drängt sich gerade Deutschland schon wieder so nach vorne? Was steht im Zeugnis von Deutschland? Geschichtsunterricht: nicht teilgenommen
Alles, wofür Deutschland einmal stand, für Frieden und Diplomatie, scheint einer allgemeinen Kriegslüsternheit des Polit-Büros gewichen zu sein, obwohl die Arsenale leer sind (Gottseidank!). Eine Aufrüstung sowohl logistisch, personell als auch materialmäßig würde mindestens 10 Jahre dauern. Da kann man nur hoffen, dass Putin so lange wartet, wo doch aus allen Propagandarohren geschossen wird, dass er seine imperialistischen Phantasien nach der Ukraine weiter in Richtung Europa ausleben will. Erst nach Polen und dann mit dem Trampolin von Brandenburg aus direkt nach Berlin. Das war’s. Dabei brauchen wir gar keinen Feind von außen. Deutschland ist ja bereits mit der BRD im Krieg.
Man spekuliert auf einen europäischen Schutzschild mit Frankreich als Land mit Atomwaffen. Wie lächerlich ist das denn? Das erinnert an einen Yorkshire-Terrier, der ein Pferd anbellt. Die immer noch gültige Feindstaaten-Klausel scheint für alle zu gelten, nur nicht für die, die sie betrifft, also Deutschland. Sie ist durch den 2 + 4 – Vertrag nicht aufgehoben worden, weil der kein Friedensvertrag ist.
Trump spricht davon, seine Truppen aus Europa, aus Deutschland abzuziehen. Es kursieren Gerüchte, dass er gar die NATO verlassen könnte. Dann steht Deutschland völlig blank da – stets aufs Äußerste zur Entschlossenheit bereit! Panik im Hühnerstall, weil der Fuchs in der Nähe gesehen wurde. Und statt Überlegungen in Richtung Neutralität anzustellen, was gut zu Deutschland, im Verbund mit Österreich und der Schweiz als deutschsprachigen Kulturraum passen würde, überlegt man, wie man die Arbeiter der niedergehenden Autoindustrie in der Rüstungsindustrie anschlussverwenden kann. Es ist alles nur noch irre.
Wer Pazifist und für den Frieden ist, delegitimiert den Staat, ist reeeeechts. Ja, wo sind wir denn inzwischen gelandet? Im Emsland macht die Polizei folgende Ansage durch einen Lautsprecher: „Beachten Sie die Beschränkungen. Ausrufe, wie „Stoppt das Morden“, „Stoppt den Krieg“ und weiterfolgend, haben zu unterbleiben.“
Vielleicht spekuliert man ja darauf, dass es eine neue Migrationswelle nach Europa gibt. Diesmal von denen, die von der US-Regierung als Deep State-Angehörige aufgespürt werden. Mit ihrem Geld und Einfluss kämen sie den Großmanns-Phantasien der Europäer gerade recht. Herzlich Willkommen, ihr Deep-State-Fachkräfte!
Mit den zukünftig in der deutschen Regierung befindlichen Alt-Parteien wird es ein „Weiter so“ in Richtung Niedergang geben. Ein weiteres Zeichen dafür, dass Deutschland von Masochisten gelenkt wird. Wie man an den Wahlergebnissen sehen kann, befindet sich ein großer Teil der Bevölkerung immer noch im Dauer-Tiefschlaf. Und der wache Rest schaut ohnmächtig zu, wie die Katastrophe weiter ihren Lauf nimmt. Die einzige friedliche Möglichkeit, diesem schadenbringenden Treiben ein Ende zu bereiten, wäre dem Staat den Geldhahn zuzudrehen: Steuerzahlungs-Verweigerung, Einstellung der Zwangsgebühren für den Staats-Propaganda-Funk, Verweigerung der Kammer-Zwangs-Beiträge, doch da landet man im Knast. Da stößt die vielgepriesene Freiheit in „Unseredemokratie“ an ihre Grenzen.
Und dass all die Missstände ja nicht an die breite Öffentlichkeit gelangen, wird fleißig zensiert und zum Denunzieren angeregt, wozu es Menschen braucht, die sich dafür hergeben, und die es aber offensichtlich zu geben scheint. Der Digital Services Act ist nichts weiter, als die Weiterentwicklung des Fernsehens der DDR, oder noch schlimmeres. Jüngst erst wurde eine Telefonseelsorge für diejenigen eingerichtet, die auf dem Pfad des tugendhaft betreuten Denkens vom Weg abgekommen sind. Bereue und Dir wird vergeben!
Bei den vorletzten Wahlen mussten die Bürger einen Maulkorb tragen, bei der jüngsten Bundestagswahl hatten sie diesen bereits in den Kopf implantiert, da fast die Hälfte der Deutschen meint, ihre Meinung nicht mehr frei äußern zu können. Wenn das mal keinen Einfluss auf die Wahlentscheidung hatte.
Man kann recht pessimistisch sein, dass in absehbarer Zeit wieder die Vernunft Einzug in die Köpfe der Verantwortlichen hält, daher ist zu vermuten, dass Europa erst komplett implodieren muss, bevor ein Neuanfang möglich sein wird. Man kann aber auch optimistisch sein, da Deutschland, in der EU der größte Geldgeber, derzeit fleißig daran arbeitet, dass der Karren tiefst möglich in den Dreck gefahren wird. Fein, weg mit dem Brüsseler Bürokratie-Monster und zurück zur Europäischen Wirtschaftsgemeinschaft. Die Sommerzeit, die Gurken-Krümmungs-Verordnung und die Tetra-Pak-Deckel-Ehe würde man wohl kaum vermissen.
Die zahlreichen Universal-Dilettanten und Kriegs-Maulhelden in ganz Europa werden ihren Teil dazu beitragen, den Deppen-Status in der Welt zu manifestieren.
Nicht ganz so rosig wäre es, wenn die US-Deep-State-Migranten auf die Idee kämen, in Europa Fuß fassen zu wollen. Das wäre dann eher ein Neuanfang mit einer E-ID, dem digitalen Bargeld, einem Social-Credit-System, also den feuchten Träumen des WEFs, 15-Minuten-Städten, KI-gesteuerter Mobilität und totaler Versklavung durch 24/7/365-Überwachung. Die Kriminell-Kommissarin, das Röschen in Brüssel, arbeitet auch hier schon emsig wie ein Bienchen. Wenn hinter all dem Trump-Getöse dasselbe steckt, haben wir sowieso verloren.
Europa befindet sich am Scheideweg. Quo vadis?
Die breite Masse fühlt sich in ihrem Weltbild „verunsichert“. Eingeschüchtert von Messer-Fachkräften und Autos, die trotz Fahrer einfach so in Menschenmengen rasen, weil sie es wollen. Ob ein System hinter den Anschlägen steckt, oder nicht, spielt gar keine Rolle. Es passiert. Was, wenn der Staat sagt, jetzt ist Schluss, wir greifen durch. Zum Schutze und zur Sicherheit der Bevölkerung führen wir eine persönliche ID ein, als Abschreckungsmaßnahme, damit ja kein Irrer mehr auch nur auf die Idee kommt, so einen Anschlag verüben zu wollen.
Wollt ihr zu eurem eigenen Schutz die totale Überwachung? „JAAAAAAA!“
Die positiv Gestimmten behaupten zwar, es würden immer mehr Menschen wach werden, doch obwohl die Wecker nun schon seit 5 Jahren ununterbrochen laut klingeln, geht das viel zu langsam. Bis auch Lieschen Müller aus Hinterdeppendorf verstanden hat, dass wir nach allen Regeln der Kunst belogen und betrogen werden, ist es wahrscheinlich schon längst soweit, dass die Falle zugeschnappt ist.
Und dann wird das Geheule groß sein: „Ach hätten wir doch mal…“ Ja, wenn so viele nicht immer noch viel zu bequem, behäbig und träge wären, hätten wir schon längst die Pfeifen in unseren europäischen Parlamenten inklusive des Affen-Zirkus in Brüssel in die Wüste geschickt.
Ja, wir brauchen eine Revolution, aber eine geistige! Wie bekommen wir die Denkvergiftung durch jahrzehntelanges Starren auf die Inhalte der öffentlich-rechtlichen Anstalt für Propaganda und Volksverblödung als Gehirnwaschanlage aus den Köpfen der Leute wieder heraus?
Lieber wartet man auf den Erlöser, der es schon richten wird. Ich habe ja schließlich gewählt, mehr kann ich nicht tun. Nein, der kommt nicht. Der Fritzefanzler ist es leider auch nicht. Der wechselt seine Meinung schneller, als man ein Paar Socken an- und ausgezogen hat. Da nutzen auch seine markig akzentuierten Sprechabsonderungen nichts. Schon jetzt muss man sein Bild umdrehen, damit die Mundwinkel einmal nach oben zeigen. Warum ist er traurig? Geht es dem Sauerländer nicht schnell genug, den Rest von Deutschland in Essig einzulegen, damit dieses Land vollkommen in ein trefflich schmeckendes Glas Gewürzgurken verwandelt wird?
Es wäre an uns, uns unserer Kraft als Souverän bewusst zu werden und die Schritte einzuleiten, die nötig sind, um ein friedliches und einträgliches miteinander der Nationen zu leben. Die Menschen wollen keinen Krieg, es sind immer die Staaten. In Rumänien, in Bulgarien sind die Menschen massenweise auf der Straße und drücken ihren Protest aus. In Deutschland geht das nicht. Man hat ja noch die Kartoffeln auf dem Herd und kann solange nicht weg. Es sei denn, man kann ein paar Euro dazuverdienen, das ist dann was anderes. Und endlich ist dann auch noch einmal was im Leben der enkellosen Großmutter los.
Krieg ist nur die Durchsetzung von Politik mit anderen Mitteln. Es ging und geht nie um Menschenleben, sondern um das erbarmungslose Durchsetzen von staatlichen Interessen, die gefälligst im schlimmsten Fall vom dämlichen Volk als Kanonenfutter umzusetzen sind.
Nach den Impfverweigerern kommen vielleicht bald die Kriegsdienstverweigerer in den Fokus. Ich soll mein Leben für ein Land auf’s Spiel setzen, das einen Bockmist nach dem anderen baut? Bin ich lebensmüde?
Und obendrein zahlt der brave Bürger auch noch die Zeche, mit seinem sauer verdienten Geld durch legalisierten Steuerraub. Jeder würde wohl gerne Steuern zahlen, wenn das Geld sinnvoll verwendet würde. Ein Hochrüsten gehört ganz sicher nicht dazu. Geschickteres Ausbeuten von Staatsseite geht nicht, und dümmer nicht von Seiten der Bevölkerung, die sich das gefallen lässt.
Die Demokratie-Simulation hat bislang recht gut funktioniert. Es bleibt zu hoffen, dass es ein guter Wind ist, der da von Westen über den Atlantik nach Europa weht und diese ganzen verklebten Gehirne einmal so richtig durchbläst. Die Ereignisse überschlagen sich derzeit, wer weiß?
-
 @ 97c70a44:ad98e322
2025-03-05 18:09:05
@ 97c70a44:ad98e322
2025-03-05 18:09:05So you've decided to join nostr! Some wide-eyed fanatic has convinced you that the "sun shines every day on the birds and the bees and the cigarette trees" in a magical land of decentralized, censorship-resistant freedom of speech - and it's waiting just over the next hill.
But your experience has not been all you hoped. Before you've even had a chance to upload your AI-generated cyberpunk avatar or make up exploit codenames for your pseudonym's bio, you've been confronted with a new concept that has left you completely nonplussed.
It doesn't help that this new idea might be called by any number of strange names. You may have been asked to "paste your nsec", "generate a private key", "enter your seed words", "connect with a bunker", "sign in with extension", or even "generate entropy". Sorry about that.
All these terms are really referring to one concept under many different names: that of "cryptographic identity".
Now, you may have noticed that I just introduced yet another new term which explains exactly nothing. You're absolutely correct. And now I'm going to proceed to ignore your complaints and talk about something completely different. But bear with me, because the juice is worth the squeeze.
Identity
What is identity? There are many philosophical, political, or technical answers to this question, but for our purposes it's probably best to think of it this way:
Identity is the essence of a thing. Identity separates one thing from all others, and is itself indivisible.
This definition has three parts:
- Identity is "essential": a thing can change, but its identity cannot. I might re-paint my house, replace its components, sell it, or even burn it down, but its identity as something that can be referred to - "this house" - is durable, even outside the boundaries of its own physical existence.
- Identity is a unit: you can't break an identity into multiple parts. A thing might be composed of multiple parts, but that's only incidental to the identity of a thing, which is a concept, not a material thing.
- Identity is distinct: identity is what separates one thing from all others - the concept of an apple can't be mixed with that of an orange; the two ideas are distinct. In the same way, a single concrete apple is distinct in identity from another - even if the component parts of the apple decompose into compost used to grow more apples.
Identity is not a physical thing, but a metaphysical thing. Or, in simpler terms, identity is a "concept".
I (or someone more qualified) could at this point launch into a Scholastic tangent on what "is" is, but that is, fortunately, not necessary here. The kind of identities I want to focus on here are not our actual identities as people, but entirely fictional identities that we use to extend our agency into the digital world.
Think of it this way - your bank login does not represent you as a complete person. It only represents the access granted to you by the bank. This access is in fact an entirely new identity that has been associated with you, and is limited in what it's useful for.
Other examples of fictional identities include:
- The country you live in
- Your social media persona
- Your mortgage
- Geographical coordinates
- A moment in time
- A chess piece
Some of these identites are inert, for example points in space and time. Other identies have agency and so are able to act in the world - even as fictional concepts. In order to do this, they must "authenticate" themselves (which means "to prove they are real"), and act within a system of established rules.
For example, your D&D character exists only within the collective fiction of your D&D group, and can do anything the rules say. Its identity is authenticated simply by your claim as a member of the group that your character in fact exists. Similarly, a lawyer must prove they are a member of the Bar Association before they are allowed to practice law within that collective fiction.
"Cryptographic identity" is simply another way of authenticating a fictional identity within a given system. As we'll see, it has some interesting attributes that set it apart from things like a library card or your latitude and longitude. Before we get there though, let's look in more detail at how identities are authenticated.
Certificates
Merriam-Webster defines the verb "certify" as meaning "to attest authoritatively". A "certificate" is just a fancy way of saying "because I said so". Certificates are issued by a "certificate authority", someone who has the authority to "say so". Examples include your boss, your mom, or the Pope.
This method of authentication is how almost every institution authenticates the people who associate with it. Colleges issue student ID cards, governments issue passports, and websites allow you to "register an account".
In every case mentioned above, the "authority" creates a closed system in which a document (aka a "certificate") is issued which serves as a claim to a given identity. When someone wants to access some privileged service, location, or information, they present their certificate. The authority then validates it and grants or denies access. In the case of an international airport, the certificate is a little book printed with fancy inks. In the case of a login page, the certificate is a username and password combination.
This pattern for authentication is ubiquitous, and has some very important implications.
First of all, certified authentication implies that the issuer of the certificate has the right to exclusive control of any identity it issues. This identity can be revoked at any time, or its permissions may change. Your social credit score may drop arbitrarily, or money might disappear from your account. When dealing with certificate authorities, you have no inherent rights.
Second, certified authentication depends on the certificate authority continuing to exist. If you store your stuff at a storage facility but the company running it goes out of business, your stuff might disappear along with it.
Usually, authentication via certificate authority works pretty well, since an appeal can always be made to a higher authority (nature, God, the government, etc). Authorities also can't generally dictate their terms with impunity without losing their customers, alienating their constituents, or provoking revolt. But it's also true that certification by authority creates an incentive structure that frequently leads to abuse - arbitrary deplatforming is increasingly common, and the bigger the certificate authority, the less recourse the certificate holder (or "subject") has.
Certificates also put the issuer in a position to intermediate relationships that wouldn't otherwise be subject to their authority. This might take the form of selling user attention to advertisers, taking a cut of financial transactions, or selling surveillance data to third parties.
Proliferation of certificate authorities is not a solution to these problems. Websites and apps frequently often offer multiple "social sign-in" options, allowing their users to choose which certificate authority to appeal to. But this only piles more value into the social platform that issues the certificate - not only can Google shut down your email inbox, they can revoke your ability to log in to every website you used their identity provider to get into.
In every case, certificate issuance results in an asymmetrical power dynamic, where the issuer is able to exert significant control over the certificate holder, even in areas unrelated to the original pretext for the relationship between parties.
Self-Certification
But what if we could reverse this power dynamic? What if individuals could issue their own certificates and force institutions to accept them?

Ron Swanson's counterexample notwithstanding, there's a reason I can't simply write myself a parking permit and slip it under the windshield wiper. Questions about voluntary submission to legitimate authorities aside, the fact is that we don't have the power to act without impunity - just like any other certificate authority, we have to prove our claims either by the exercise of raw power or by appeal to a higher authority.
So the question becomes: which higher authority can we appeal to in order to issue our own certificates within a given system of identity?
The obvious answer here is to go straight to the top and ask God himself to back our claim to self-sovereignty. However, that's not how he normally works - there's a reason they call direct acts of God "miracles". In fact, Romans 13:1 explicitly says that "the authorities that exist have been appointed by God". God has structured the universe in such a way that we must appeal to the deputies he has put in place to govern various parts of the world.
Another tempting appeal might be to nature - i.e. the material world. This is the realm in which we most frequently have the experience of "self-authenticating" identities. For example, a gold coin can be authenticated by biting it or by burning it with acid. If it quacks like a duck, walks like a duck, and looks like a duck, then it probably is a duck.
In most cases however, the ability to authenticate using physical claims depends on physical access, and so appeals to physical reality have major limitations when it comes to the digital world. Captchas, selfies and other similar tricks are often used to bridge the physical world into the digital, but these are increasingly easy to forge, and hard to verify.
There are exceptions to this rule - an example of self-certification that makes its appeal to the physical world is that of a signature. Signatures are hard to forge - an incredible amount of data is encoded in physical signatures, from strength, to illnesses, to upbringing, to personality. These can even be scanned and used within the digital world as well. Even today, most contracts are sealed with some simulacrum of a physical signature. Of course, this custom is quickly becoming a mere historical curiosity, since the very act of digitizing a signature makes it trivially forgeable.
So: transcendent reality is too remote to subtantiate our claims, and the material world is too limited to work within the world of information. There is another aspect of reality remaining that we might appeal to: information itself.
Physical signatures authenticate physical identities by encoding unique physical data into an easily recognizable artifact. To transpose this idea to the realm of information, a "digital signature" might authenticate "digital identities" by encoding unique "digital data" into an easily recognizable artifact.
Unfortunately, in the digital world we have the additional challenge that the artifact itself can be copied, undermining any claim to legitimacy. We need something that can be easily verified and unforgeable.
Digital Signatures
In fact such a thing does exist, but calling it a "digital signature" obscures more than it reveals. We might just as well call the thing we're looking for a "digital fingerprint", or a "digital electroencephalogram". Just keep that in mind as we work our way towards defining the term - we are not looking for something looks like a physical signature, but for something that does the same thing as a physical signature, in that it allows us to issue ourselves a credential that must be accepted by others by encoding privileged information into a recognizable, unforgeable artifact.
With that, let's get into the weeds.
An important idea in computer science is that of a "function". A function is a sort of information machine that converts data from one form to another. One example is the idea of "incrementing" a number. If you increment 1, you get 2. If you increment 2, you get 3. Incrementing can be reversed, by creating a complementary function that instead subtracts 1 from a number.
A "one-way function" is a function that can't be reversed. A good example of a one-way function is integer rounding. If you round a number and get
5, what number did you begin with? It's impossible to know - 5.1, 4.81, 5.332794, in fact an infinite number of numbers can be rounded to the number5. These numbers can also be infinitely long - for example rounding PI to the nearest integer results in the number3.A real-life example of a useful one-way function is
sha256. This function is a member of a family of one-way functions called "hash functions". You can feed as much data as you like intosha256, and you will always get 256 bits of information out. Hash functions are especially useful because collisions between outputs are very rare - even if you change a single bit in a huge pile of data, you're almost certainly going to get a different output.Taking this a step further, there is a whole family of cryptographic one-way "trapdoor" functions that act similarly to hash functions, but which maintain a specific mathematical relationship between the input and the output which allows the input/output pair to be used in a variety of useful applications. For example, in Elliptic Curve Cryptography, scalar multiplication on an elliptic curve is used to derive the output.
"Ok", you say, "that's all completely clear and lucidly explained" (thank you). "But what goes into the function?" You might expect that because of our analogy to physical signatures we would have to gather an incredible amount of digital information to cram into our cryptographic trapdoor function, mashing together bank statements, a record of our heartbeat, brain waves and cellular respiration. Well, we could do it that way (maybe), but there's actually a much simpler solution.
Let's play a quick game. What number am I thinking of? Wrong, it's 82,749,283,929,834. Good guess though.
The reason we use signatures to authenticate our identity in the physical world is not because they're backed by a lot of implicit physical information, but because they're hard to forge and easy to validate. Even so, there is a lot of variation in a single person's signature, even from one moment to the next.
Trapdoor functions solve the validation problem - it's trivially simple to compare one 256-bit number to another. And randomness solves the problem of forgeability.
Now, randomness (A.K.A. "entropy") is actually kind of hard to generate. Random numbers that don't have enough "noise" in them are known as "pseudo-random numbers", and are weirdly easy to guess. This is why Cloudflare uses a video stream of their giant wall of lava lamps to feed the random number generator that powers their CDN. For our purposes though, we can just imagine that our random numbers come from rolling a bunch of dice.
To recap, we can get a digital equivalent of a physical signature (or fingerprint, etc) by 1. coming up with a random number, and 2. feeding it into our chosen trapdoor function. The random number is called the "private" part. The output of the trapdoor function is called the "public" part. These two halves are often called "keys", hence the terms "public key" and "private key".
And now we come full circle - remember about 37 years ago when I introduced the term "cryptographic identity"? Well, we've finally arrived at the point where I explain what that actually is.
A "cryptographic identity" is identified by a public key, and authenticated by the ability to prove that you know the private key.
Notice that I didn't say "authenticated by the private key". If you had to reveal the private key in order to prove you know it, you could only authenticate a public key once without losing exclusive control of the key. But cryptographic identities can be authenticated any number of times because the certification is an algorithm that only someone who knows the private key can execute.
This is the super power that trapdoor functions have that hash functions don't. Within certain cryptosystems, it is possible to mix additional data with your private key to get yet another number in such a way that someone else who only knows the public key can prove that you know the private key.
For example, if my secret number is
12, and someone tells me the number37, I can "combine" the two by adding them together and returning the number49. This "proves" that my secret number is12. Of course, addition is not a trapdoor function, so it's trivially easy to reverse, which is why cryptography is its own field of knowledge.What's it for?
If I haven't completely lost you yet, you might be wondering why this matters. Who cares if I can prove that I made up a random number?
To answer this, let's consider a simple example: that of public social media posts.
Most social media platforms function by issuing credentials and verifying them based on their internal database. When you log in to your Twitter (ok, fine, X) account, you provide X with a phone number (or email) and password. X compares these records to the ones stored in the database when you created your account, and if they match they let you "log in" by issuing yet another credential, called a "session key".
Next, when you "say" something on X, you pass along your session key and your tweet to X's servers. They check that the session key is legit, and if it is they associate your tweet with your account's identity. Later, when someone wants to see the tweet, X vouches for the fact that you created it by saying "trust me" and displaying your name next to the tweet.
In other words, X creates and controls your identity, but they let you use it as long as you can prove that you know the secret that you agreed on when you registered (by giving it to them every time).
Now pretend that X gets bought by someone even more evil than Elon Musk (if such a thing can be imagined). The new owner now has the ability to control your identity, potentially making it say things that you didn't actually say. Someone could be completely banned from the platform, but their account could be made to continue saying whatever the owner of the platform wanted.
In reality, such a breach of trust would quickly result in a complete loss of credibility for the platform, which is why this kind of thing doesn't happen (at least, not that we know of).
But there are other ways of exploiting this system, most notably by censoring speech. As often happens, platforms are able to confiscate user identities, leaving the tenant no recourse except to appeal to the platform itself (or the government, but that doesn't seem to happen for some reason - probably due to some legalese in social platforms' terms of use). The user has to start completely from scratch, either on the same platform or another.
Now suppose that when you signed up for X instead of simply telling X your password you made up a random number and provided a cryptographic proof to X along with your public key. When you're ready to tweet (there's no need to issue a session key, or even to store your public key in their database) you would again prove your ownership of that key with a new piece of data. X could then publish that tweet or not, along with the same proof you provided that it really came from you.
What X can't do in this system is pretend you said something you didn't, because they don't know your private key.
X also wouldn't be able to deplatform you as effectively either. While they could choose to ban you from their website and refuse to serve your tweets, they don't control your identity. There's nothing they can do to prevent you from re-using it on another platform. Plus, if the system was set up in such a way that other users followed your key instead of an ID made up by X, you could switch platforms and keep your followers. In the same way, it would also be possible to keep a copy of all your tweets in your own database, since their authenticity is determined by your digital signature, not X's "because I say so".
This new power is not just limited to social media either. Here are some other examples of ways that self-issued cryptographic identites transform the power dynamic inherent in digital platforms:
- Banks sometimes freeze accounts or confiscate funds. If your money was stored in a system based on self-issued cryptographic keys rather than custodians, banks would not be able to keep you from accessing or moving your funds. This system exists, and it's called bitcoin.
- Identity theft happens when your identifying information is stolen and used to take out a loan in your name, and without your consent. The reason this is so common is because your credentials are not cryptographic - your name, address, and social security number can only be authenticated by being shared, and they are shared so often and with so many counterparties that they frequently end up in data breaches. If credit checks were authenticated by self-issued cryptographic keys, identity theft would cease to exist (unless your private key itself got stolen).
- Cryptographic keys allow credential issuers to protect their subjects' privacy better too. Instead of showing your ID (including your home address, birth date, height, weight, etc), the DMV could sign a message asserting that the holder of a given public key indeed over 21. The liquor store could then validate that claim, and your ownership of the named key, without knowing anything more about you. Zero-knowledge proofs take this a step further.
In each of these cases, the interests of the property owner, loan seeker, or customer are elevated over the interests of those who might seek to control their assets, exploit their hard work, or surveil their activity. Just as with personal privacy, freedom of speech, and Second Amendment rights the individual case is rarely decisive, but in the aggregate realigned incentives can tip the scale in favor of freedom.
Objections
Now, there are some drawbacks to digital signatures. Systems that rely on digital signatures are frequently less forgiving of errors than their custodial counterparts, and many of their strengths have corresponding weaknesses. Part of this is because people haven't yet developed an intuition for how to use cryptographic identities, and the tools for managing them are still being designed. Other aspects can be mitigated through judicious use of keys fit to the problems they are being used to solve.
Below I'll articulate some of these concerns, and explore ways in which they might be mitigated over time.
Key Storage
Keeping secrets is hard. "A lie can travel halfway around the world before the truth can get its boots on", and the same goes for gossip. Key storage has become increasingly important as more of our lives move online, to the extent that password managers have become almost a requirement for keeping track of our digital lives. But even with good password management, credentials frequently end up for sale on the dark web as a consequence of poorly secured infrastructure.
Apart from the fact that all of this is an argument for cryptographic identities (since keys are shared with far fewer parties), it's also true that the danger of losing a cryptographic key is severe, especially if that key is used in multiple places. Instead of hackers stealing your Facebook password, they might end up with access to all your other social media accounts too!
Keys should be treated with the utmost care. Using password managers is a good start, but very valuable keys should be stored even more securely - for example in a hardware signing device. This is a hassle, and something additional to learn, but is an indispensable part of taking advantage of the benefits associated with cryptographic identity.
There are ways to lessen the impact of lost or stolen secrets, however. Lots of different techniques exist for structuring key systems in such a way that keys can be protected, invalidated, or limited. Here are a few:
- Hierarchical Deterministic Keys allow for the creation of a single root key from which multiple child keys can be generated. These keys are hard to link to the parent, which provides additional privacy, but this link can also be proven when necessary. One limitation is that the identity system has to be designed with HD keys in mind.
- Key Rotation allows keys to become expendable. Additional credentials might be attached to a key, allowing the holder to prove they have the right to rotate the key. Social attestations can help with the process as well if the key is embedded in a web of trust.
- Remote Signing is a technique for storing a key on one device, but using it on another. This might take the form of signing using a hardware wallet and transferring an SD card to your computer for broadcasting, or using a mobile app like Amber to manage sessions with different applications.
- Key sharding takes this to another level by breaking a single key into multiple pieces and storing them separately. A coordinator can then be used to collaboratively sign messages without sharing key material. This dramatically reduces the ability of an attacker to steal a complete key.
Multi-Factor Authentication
One method for helping users secure their accounts that is becoming increasingly common is "multi-factor authentication". Instead of just providing your email and password, platforms send a one-time use code to your phone number or email, or use "time-based one time passwords" which are stored in a password manager or on a hardware device.
Again, MFA is a solution to a problem inherent in account-based authentication which would not be nearly so prevalent in a cryptographic identity system. Still, theft of keys does happen, and so MFA would be an important improvement - if not for an extra layer of authentication, then as a basis for key rotation.
In a sense, MFA is already being researched - key shards is one way of creating multiple credentials from a single key. However, this doesn't address the issue of key rotation, especially when an identity is tied to the public key that corresponds to a given private key. There are two possible solutions to this problem:
- Introduce a naming system. This would allow identities to use a durable name, assigning it to different keys over time. The downside is that this would require the introduction of either centralized naming authorities (back to the old model), or a blockchain in order to solve Zooko's trilemma.
- Establish a chain of keys. This would require a given key to name a successor key in advance and self-invalidate, or some other process like social recovery to invalidate an old key and assign the identity to a new one. This also would significantly increase the complexity of validating messages and associating them with a given identity.
Both solutions are workable, but introduce a lot of complexity that could cause more trouble than it's worth, depending on the identity system we're talking about.
Surveillance
One of the nice qualities that systems based on cryptographic identities have is that digitally signed data can be passed through any number of untrusted systems and emerge intact. This ability to resist tampering makes it possible to broadcast signed data more widely than would otherwise be the case in a system that relies on a custodian to authenticate information.
The downside of this is that more untrusted systems have access to data. And if information is broadcast publicly, anyone can get access to it.
This problem is compounded by re-use of cryptographic identities across multiple contexts. A benefit of self-issued credentials is that it becomes possible to bring everything attached to your identity with you, including social context and attached credentials. This is convenient and can be quite powerful, but it also means that more context is attached to your activity, making it easier to infer information about you for advertising or surveillance purposes. This is dangerously close to the dystopian ideal of a "Digital ID".
The best way to deal with this risk is to consider identity re-use an option to be used when desirable, but to default to creating a new key for every identity you create. This is no worse than the status quo, and it makes room for the ability to link identities when desired.
Another possible approach to this problem is to avoid broadcasting signed data when possible. This could be done by obscuring your cryptographic identity when data is served from a database, or by encrypting your signed data in order to selectively share it with named counterparties.
Still, this is a real risk, and should be kept in mind when designing and using systems based on cryptographic identity. If you'd like to read more about this, please see this blog post.
Making Keys Usable
You might be tempted to look at that list of trade-offs and get the sense that cryptographic identity is not for mere mortals. Key management is hard, and footguns abound - but there is a way forward. With nostr, some new things are happening in the world of key management that have never really happened before.
Plenty of work over the last 30 years has gone into making key management tractable, but none have really been widely adopted. The reason for this is simple: network effect.
Many of these older key systems only applied the thinnest veneer of humanity over keys. But an identity is much richer than a mere label. Having a real name, social connections, and a corpus of work to attach to a key creates a system of keys that humans care about.
By bootstrapping key management within a social context, nostr ensures that the payoff of key management is worth the learning curve. Not only is social engagement a strong incentive to get off the ground, people already on the network are eager to help you get past any roadblocks you might face.
So if I could offer an action item: give nostr a try today. Whether you're in it for the people and their values, or you just want to experiment with cryptographic identity, nostr is a great place to start. For a quick introduction and to securely generate keys, visit njump.me.
Thanks for taking the time to read this post. I hope it's been helpful, and I can't wait to see you on nostr!
-
 @ 6b0a60cf:b952e7d4
2025-03-06 02:45:45
@ 6b0a60cf:b952e7d4
2025-03-06 02:45:45とあるSNSで海外の相互さん(以降、Aさんと呼ぶ)からDMで相談されたことがあって、思ったことをつらつらと書いてみる。
非公開の場での相談なので多少ぼかしを入れるけど。事の経緯
発端は、Aさんの友人が作品に日本人作者の素材を使用しようとしていて、その利用規約を翻訳して読んだらうまく翻訳されなくて理解が正しいのかわからない、なので間違いが無いか確認してほしい、という相談だった。
あー、確かに日本語特有の回りくどい表現があるねー、と思いながらバシッと簡潔に意訳してお伝えしたところ、スッキリ理解していただけたらしく一件落着となった。独自ライセンス文化
しかしまあ、創作界隈における作品・素材の利用規約というものは総じて長くて細かい。
ジャンルによるのかもしれないけれど。
自分は絵や音を創ることは無いがプログラムのコードを書く趣味はあるのでプログラム向けのライセンスを利用している。MITとかGPLとかいうやつ。
創作向けであればCCライセンスが適しているだろう。しかしこれがなかなか広まらない。
杓子定規のライセンスでは表しきれないような特別な希望があるのだろう。
そして独自ライセンスが跋扈することとなる。NO MORE 映画泥棒
特に気になるのが、「泥棒をしてはいけません」レベルの注意書きが散見されるのだ。
わざわざライセンスに書くことではない。あなたが警告するまでもなく、違法な行為は処罰される。
でも、たぶん効果があるからこういうのが広まるのだろう。
「泥棒してはいけないって書いてないから泥棒しました」というレベルの利用者が存在するのだろう。
そういう人は書いてあっても読んでないか、理屈をこねて泥棒するんだろうと思うけれども。その術はオレに効く
で、そういう警告文が魔除けの札のごとくびっしり貼られていると、こちらにやましい心が無くても、ちょっとこの素材は利用しないほうがよさそうだな……と思って引き返してしまうことがある。
SNSで可愛い絵を見て、作者さんをフォローしようと思ったら「無断転載禁止」みたいなのがプロフにずらずら書いてあって「おっと……」みたいに引き返すことがあるが、それに似ている。
きっと過去によくない体験をしてしまって、そのようにプロフに書くことでそれが改善するという実体験があって、そうなっているのだろうと推測している。異文化の壁を超えて
冒頭で話したAさんはきわめて紳士的な方であり、日本文化に対してもよく理解しようと努めてくれるので、話が通じやすくて助かったし、件の素材についても臆すること無く使用することになりそうだった。
ただ魔除けの札が効かないような魑魅魍魎にはいくら札を貼っても意味がないし、実際の悪魔祓いの効果と善良な利用者をも祓ってしまう機会損失(?)を比べて合理的なのだろうか、と考えたりしたのでした。オチは無い。ライセンス
この文章は CC0 1.0 でライセンスします。
Nostrイベントとして公開する以上はNIPsに従う範囲内で自由に利用されることを望みます。
NIPsに違反したご利用は他のクライアントの利用者にご迷惑になるのでご遠慮いただくことを希望します。^1 -
 @ 8d34bd24:414be32b
2025-03-05 16:52:58
@ 8d34bd24:414be32b
2025-03-05 16:52:58Sometimes I wonder why I write posts like this. This is not the way to gain a big following, but then again, that is not my goal. My goal is to share Jesus with anyone who will listen, to faithfully speak whatever truth I feel God is leading me to share, and to teach the inerrant word of God in order to draw people, both believers and not yet believers, closer to Jesus. I trust God to use my words in whatever way He sees best. If it only reaches a few, that is OK by me. If somehow this substack starts reaching a vast audience, then praise God for that!
Today, I am writing about a hard truth. The Bible contains a number of hard truths that most people don’t want to believe, but which our Creator God has stated as truth. None of us likes being called a sinner, but the Bible says:
as it is written, “There is none righteous, not even one. (Romans 3:10)
As hard as the truth that we are all sinners is, a much harder truth is that not everyone gets to go to Heaven. Some people are destined for Hell. I am going to investigate some verses that illuminate this truth.
Ironically, most people have two contradictory thoughts. Most people wonder why God allows so much evil in the world. If He is truly sovereign, why doesn’t He stop evil? At the same time they wonder why a loving God would send anyone to Hell. We can’t expect God to stop and punish evil, but not send some people to Hell. We can’t have it both ways.
The Lord is not slow about His promise, as some count slowness, but is patient toward you, not wishing for any to perish but for all to come to repentance. (2 Peter 3:9)
This verse explains the basic facts of how God’s holiness is reconciled with His love and mercy, but of course there is so much more. If God is truly sovereign over all, then why is there any evil? Why does anyone sin? Why is there pain and suffering?
The Lord has made everything for its own purpose,\ Even the wicked for the day of evil.\ Everyone who is proud in heart is an abomination to the Lord;\ Assuredly, he will not be unpunished.\ By lovingkindness and truth iniquity is atoned for,\ And by the fear of the Lord one keeps away from evil. (Proverbs 16:4-6) {emphasis mine}
Everyone and everything was made for God’s own purpose. As our Creator, He has the right to make each of us for whatever purpose He desires. The creature has no right to question the Creator and His purpose.
Then I went down to the potter’s house, and there he was, making something on the wheel. But the vessel that he was making of clay was spoiled in the hand of the potter; so he remade it into another vessel, as it pleased the potter to make.
Then the word of the Lord came to me saying, “Can I not, O house of Israel, deal with you as this potter does?” declares the Lord. “Behold, like the clay in the potter’s hand, so are you in My hand, O house of Israel. At one moment I might speak concerning a nation or concerning a kingdom to uproot, to pull down, or to destroy it; if that nation against which I have spoken turns from its evil, I will relent concerning the calamity I planned to bring on it. Or at another moment I might speak concerning a nation or concerning a kingdom to build up or to plant it; if it does evil in My sight by not obeying My voice, then I will think better of the good with which I had promised to bless it. (Jeremiah 18:3-10) {emphasis mine}
But the Bible says it even goes beyond God directly responding to our choices. The God of the Bible is creator and sovereign over all. Nothing happens contrary to His will.
So then He has mercy on whom He desires, and He hardens whom He desires.
You will say to me then, “Why does He still find fault? For who resists His will?” On the contrary, who are you, O man, who answers back to God? The thing molded will not say to the molder, “Why did you make me like this,” will it? Or does not the potter have a right over the clay, to make from the same lump one vessel for honorable use and another for common use? What if God, although willing to demonstrate His wrath and to make His power known, endured with much patience vessels of wrath prepared for destruction? And He did so to make known the riches of His glory upon vessels of mercy, which He prepared beforehand for glory, even us, whom He also called, not from among Jews only, but also from among Gentiles. (Romans 9:18-24) {emphasis mine}
The above passage speaks a very uncomfortable truth. We don’t like thinking we don’t have full and complete free-will to do whatever we want and to determine our future, but it isn’t that simple. The Bible says specifically that some are “prepared for destruction” and others are “prepared beforehand for glory.”
For by grace you have been saved through faith; and that not of yourselves, it is the gift of God; not as a result of works, so that no one may boast. For we are His workmanship, created in Christ Jesus for good works, which God prepared beforehand so that we would walk in them. (Ephesians 2:8-10) {emphasis mine}
We aren’t saved because we are smarter than all of the people who didn’t choose Jesus. We aren’t wiser than those who chose their own path rather than the path designed by God. We are saved by God as a gift. He called those who were dead in their sins to life in him. The dead can’t choose anything. We all must be made spiritually alive so we can follow Him. Only Jesus does that. We can’t make ourselves alive in Him.
Every believer needs to thank Jesus daily for the miracle of spiritual life in Him that has been given to us despite us not deserving it or choosing it.
In this is love, not that we loved God, but that He loved us and sent His Son to be the propitiation for our sins. (1 John 4:10)
and
We love, because He first loved us. (1 John 4:19)
Jesus acted first, choosing us, and we responded, not that we chose Him and He loved us because of our choice.
I’m sure many of my readers are cringing at this Biblical truth. We all try to make God’s word say something else because we don’t like feeling out of control. We don’t like to think that someone else is smarter, stronger, or more in control of our lives than ourselves. Still, being made to follow Jesus is the greatest blessing a person can receive.
Trust in the Lord with all your heart\ And do not lean on your own understanding.\ In all your ways acknowledge Him,\ And He will make your paths straight.\ Do not be wise in your own eyes;\ Fear the Lord and turn away from evil.\ It will be healing to your body\ And refreshment to your bones. (Proverbs 3:5-8)
We don’t have to fully understand God’s truth, but we do need to accept it.
May God guide you in the truth through His God breathed word, so we may serve Him faithfully and submit fully to His authority and His will to the glory of His majesty.
Trust Jesus