-

@ 39cc53c9:27168656
2025-03-30 05:54:53
> [Read the original blog post](https://blog.kycnot.me/p/kyc-no-thanks)
Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
## Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% [^1] – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% [^1] of less-than-careful criminals.
## KYC? Not you.
> KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. [^2]
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
## You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
## Your identity has been stolen
KYC data has been found to be for sale on many dark net markets[^3]. Exchanges may have leaks or hacks, and such leaks contain **very** sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. [^3]
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
## (they) Know Your Coins
You may already know that **Bitcoin and most cryptocurrencies have a transparent public blockchain**, meaning that all data is shown unencrypted for everyone to see and recorded **forever**. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
## Conclusions
To sum up, **KYC does not protect individuals**; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
> Edited 20/03/2024
> * Add reference to the 1% statement on [Rights for Illusions](#rights-for-illusions) section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity [^1]
[^1]: https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/
[^2]: https://old.reddit.com/r/BitcoinBeginners/comments/k2bve1/is_kyc_bad_if_so_why/gdtc8kz
[^3]: https://www.ccn.com/hacked-customer-data-from-world-leading-cryptocurrency-exchanges-for-sale-on-the-dark-web/
-

@ 04c915da:3dfbecc9
2025-03-26 20:54:33
Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-

@ b2d670de:907f9d4a
2025-03-25 20:17:57
This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users.
## Table of Contents
1. Prerequisites
2. Initial Server Setup
3. Installing Strfry Nostr Relay
4. Configuring Your Relay
5. Setting Up TOR
6. Making Your Relay Available on TOR
7. Testing Your Setup]
8. Maintenance and Security
9. Troubleshooting
## Prerequisites
- A Debian or Ubuntu server
- Basic familiarity with command line operations (most steps are explained in detail)
- Root or sudo access to your server
## Initial Server Setup
First, let's make sure your server is properly set up and secured.
### Update Your System
Connect to your server via SSH and update your system:
```bash
sudo apt update
sudo apt upgrade -y
```
### Set Up a Basic Firewall
Install and configure a basic firewall:
```bash
sudo apt install ufw -y
sudo ufw allow ssh
sudo ufw enable
```
This allows SSH connections while blocking other ports for security.
## Installing Strfry Nostr Relay
This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the `DEPLOYMENT.md` document in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps [here](https://github.com/hoytech/strfry/blob/master/docs/DEPLOYMENT.md).
### Install Dependencies
First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry:
```bash
sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-dev
```
Here's why each dependency is needed:
**Basic Development Tools:**
- `git`: Version control system used to clone the Strfry repository and manage code updates
- `build-essential`: Meta-package that includes compilers (gcc, g++), make, and other essential build tools
**Perl Dependencies** (used for Strfry's build scripts):
- `libyaml-perl`: Perl interface to parse YAML configuration files
- `libtemplate-perl`: Template processing system used during the build process
- `libregexp-grammars-perl`: Advanced regular expression handling for Perl scripts
**Core Libraries for Strfry:**
- `libssl-dev`: Development files for OpenSSL, used for secure connections and cryptographic operations
- `zlib1g-dev`: Compression library that Strfry uses to reduce data size
- `liblmdb-dev`: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend
- `libflatbuffers-dev`: Memory-efficient serialization library for structured data
- `libsecp256k1-dev`: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures
- `libzstd-dev`: Fast real-time compression algorithm for efficient data storage and transmission
### Clone and Build Strfry
Clone the Strfry repository:
```bash
git clone https://github.com/hoytech/strfry.git
cd strfry
```
Build Strfry:
```bash
git submodule update --init
make setup-golpe
make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores)
```
This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime.
### Install Strfry
Install the Strfry binary to your system path:
```bash
sudo cp strfry /usr/local/bin
```
This makes the `strfry` command available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions.
## Configuring Your Relay
### Create Strfry User
Create a dedicated user for running Strfry. This enhances security by isolating the relay process:
```bash
sudo useradd -M -s /usr/sbin/nologin strfry
```
The `-M` flag prevents creating a home directory, and `-s /usr/sbin/nologin` prevents anyone from logging in as this user. This is a security best practice for service accounts.
### Create Data Directory
Create a directory for Strfry's data:
```bash
sudo mkdir /var/lib/strfry
sudo chown strfry:strfry /var/lib/strfry
sudo chmod 755 /var/lib/strfry
```
This creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it.
### Configure Strfry
Copy the sample configuration file:
```bash
sudo cp strfry.conf /etc/strfry.conf
```
Edit the configuration file:
```bash
sudo nano /etc/strfry.conf
```
Modify the database path:
```
# Find this line:
db = "./strfry-db/"
# Change it to:
db = "/var/lib/strfry/"
```
Check your system's hard limit for file descriptors:
```bash
ulimit -Hn
```
Update the `nofiles` setting in your configuration to match this value (or set to 0):
```
# Add or modify this line in the config (example if your limit is 524288):
nofiles = 524288
```
The `nofiles` setting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular.
You might also want to customize your relay's information in the config file. Look for the `info` section and update it with your relay's name, description, and other details.
Set ownership of the configuration file:
```bash
sudo chown strfry:strfry /etc/strfry.conf
```
### Create Systemd Service
Create a systemd service file for managing Strfry:
```bash
sudo nano /etc/systemd/system/strfry.service
```
Add the following content:
```ini
[Unit]
Description=strfry relay service
[Service]
User=strfry
ExecStart=/usr/local/bin/strfry relay
Restart=on-failure
RestartSec=5
ProtectHome=yes
NoNewPrivileges=yes
ProtectSystem=full
LimitCORE=1000000000
[Install]
WantedBy=multi-user.target
```
This systemd service configuration:
- Runs Strfry as the dedicated strfry user
- Automatically restarts the service if it fails
- Implements security measures like `ProtectHome` and `NoNewPrivileges`
- Sets resource limits appropriate for a relay
Enable and start the service:
```bash
sudo systemctl enable strfry.service
sudo systemctl start strfry
```
Check the service status:
```bash
sudo systemctl status strfry
```
### Verify Relay is Running
Test that your relay is running locally:
```bash
curl localhost:7777
```
You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR.
## Setting Up TOR
Now let's make your relay accessible as a TOR hidden service.
### Install TOR
Install TOR from the package repositories:
```bash
sudo apt install -y tor
```
This installs the TOR daemon that will create and manage your hidden service.
### Configure TOR
Edit the TOR configuration file:
```bash
sudo nano /etc/tor/torrc
```
Scroll down to wherever you see a commented out part like this:
```
#HiddenServiceDir /var/lib/tor/hidden_service/
#HiddenServicePort 80 127.0.0.1:80
```
Under those lines, add the following lines to set up a hidden service for your relay:
```
HiddenServiceDir /var/lib/tor/strfry-relay/
HiddenServicePort 80 127.0.0.1:7777
```
This configuration:
- Creates a hidden service directory at `/var/lib/tor/strfry-relay/`
- Maps port 80 on your .onion address to port 7777 on your local machine
- Keeps all traffic encrypted within the TOR network
Create the directory for your hidden service:
```bash
sudo mkdir -p /var/lib/tor/strfry-relay/
sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/
sudo chmod 700 /var/lib/tor/strfry-relay/
```
The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys.
Restart TOR to apply changes:
```bash
sudo systemctl restart tor
```
## Making Your Relay Available on TOR
### Get Your Onion Address
After restarting TOR, you can find your onion address:
```bash
sudo cat /var/lib/tor/strfry-relay/hostname
```
This will output something like `abcdefghijklmnopqrstuvwxyz234567.onion`, which is your relay's unique .onion address. This is what you'll share with others to access your relay.
### Understanding Onion Addresses
The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key.
Your users will need to use this address with the WebSocket protocol prefix to connect: `ws://youronionaddress.onion`
## Testing Your Setup
### Test with a Nostr Client
The best way to test your relay is with an actual Nostr client that supports TOR:
1. Open your TOR browser
2. Go to your favorite client, either on clearnet or an onion service.
- Check out [this list](https://github.com/0xtrr/onion-service-nostr-clients?tab=readme-ov-file#onion-service-nostr-clients) of nostr clients available over TOR.
3. Add your relay URL: `ws://youronionaddress.onion` to your relay list
4. Try posting a note and see if it appears on your relay
- In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay.
- Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected.
Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too).
## Maintenance and Security
### Regular Updates
Keep your system, TOR, and relay updated:
```bash
# Update system
sudo apt update
sudo apt upgrade -y
# Update Strfry
cd ~/strfry
git pull
git submodule update
make -j2
sudo cp strfry /usr/local/bin
sudo systemctl restart strfry
# Verify TOR is still running properly
sudo systemctl status tor
```
Regular updates are crucial for security, especially for TOR which may have security-critical updates.
### Database Management
Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups.
### Monitoring Logs
To monitor your Strfry logs:
```bash
sudo journalctl -u strfry -f
```
To check TOR logs:
```bash
sudo journalctl -u tor -f
```
Monitoring logs helps you identify potential issues and understand how your relay is being used.
### Backup
This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server.
```bash
# Stop the relay temporarily
sudo systemctl stop strfry
# Backup the database
sudo cp -r /var/lib/strfry /path/to/backup/location
# Restart the relay
sudo systemctl start strfry
```
Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it.
```bash
sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/location
```
## Troubleshooting
### Relay Not Starting
If your relay doesn't start:
```bash
# Check logs
sudo journalctl -u strfry -e
# Verify configuration
cat /etc/strfry.conf
# Check permissions
ls -la /var/lib/strfry
```
Common issues include:
- Incorrect configuration format
- Permission problems with the data directory
- Port already in use (another service using port 7777)
- Issues with setting the nofiles limit (setting it too big)
### TOR Hidden Service Not Working
If your TOR hidden service is not accessible:
```bash
# Check TOR logs
sudo journalctl -u tor -e
# Verify TOR is running
sudo systemctl status tor
# Check onion address
sudo cat /var/lib/tor/strfry-relay/hostname
# Verify TOR configuration
sudo cat /etc/tor/torrc
```
Common TOR issues include:
- Incorrect directory permissions
- TOR service not running
- Incorrect port mapping in torrc
### Testing Connectivity
If you're having trouble connecting to your service:
```bash
# Verify Strfry is listening locally
sudo ss -tulpn | grep 7777
# Check that TOR is properly running
sudo systemctl status tor
# Test the local connection directly
curl --include --no-buffer localhost:7777
```
---
## Privacy and Security Considerations
Running a Nostr relay as a TOR hidden service provides several important privacy benefits:
1. **Network Privacy**: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay.
2. **Server Anonymity**: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting.
3. **Censorship Resistance**: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked.
4. **User Privacy**: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized.
However, there are some important considerations:
- TOR connections are typically slower than regular internet connections
- Not all Nostr clients support TOR connections natively
- Running a hidden service increases the importance of keeping your server secure
---
Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network.
For further customization and advanced configuration options, refer to the [Strfry documentation](https://github.com/hoytech/strfry).
Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network!
If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to [this list](https://github.com/0xtrr/onion-service-nostr-relays). Only add it if you plan to run a stable and available relay.
-

@ bc52210b:20bfc6de
2025-03-25 20:17:22
CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient.
This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off!
Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now.
---
**CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused!**
Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why:
* Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs).
* Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key.
**Key Differences:**
1. What’s Aggregated?
* CISA: Aggregates signatures.
* Key Aggregation: Aggregates public keys.
2. What the Verifier Needs
* CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature.
* Key Aggregation: The verifier only needs the single aggregated public key and one message.
3. When It Happens
* CISA: Used during transaction signing, when inputs are being combined into a transaction.
* MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control.
So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs!
---
**Two Flavors of CISA: Half-Agg and Full-Agg**
CISA comes in two modes:
* Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.)
* Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later.
Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg.
---
**Half Signature Aggregation (Half-Agg) Explained**
**How It Works**
Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process:
1. Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers.
2. Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature.
A Schnorr signature has two parts:
* R: A random point (32 bytes).
* s: A scalar value (32 bytes).
In Half-Agg:
* The R values from each signature are kept separate (one per input).
* The s values from all signatures are combined into a single s value.
**Why It Saves Space (~50%)**
Let’s break down the size savings with some math:
Before Aggregation:
* Each Schnorr signature = 64 bytes (32 for R + 32 for s).
* For n inputs: n × 64 bytes.
After Half-Agg:
* Keep n R values (32 bytes each) = 32 × n bytes.
* Combine all s values into one = 32 bytes.
* Total size: 32 × n + 32 bytes.
Comparison:
* Original: 64n bytes.
* Half-Agg: 32n + 32 bytes.
* For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings!
**Real-World Impact:**
Based on recent Bitcoin usage, Half-Agg could save:
* ~19.3% in space (reducing transaction size).
* ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA.
---
**Applications of Half-Agg**
Half-Agg isn’t just a cool idea—it has practical uses:
1. Transaction-wide Aggregation
* Combine all signatures within a single transaction.
* Result: Smaller transactions, lower fees.
2. Block-wide Aggregation
* Combine signatures across all transactions in a Bitcoin block.
* Result: Even bigger space savings at the blockchain level.
3. Off-chain Protocols / P2P
* Use Half-Agg in systems like Lightning Network gossip messages.
* Benefit: Efficiency without needing miners or a Bitcoin soft fork.
---
**Challenges with Half-Agg**
While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level:
1. Breaking Adaptor Signatures
* Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges.
* Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on.
2. Impact on Reorg Recovery
* In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed.
* If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery.
These challenges mean Half-Agg needs careful design, especially for block-wide use.
---
**Wrapping Up**
CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning.
But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future!
-

@ b17fccdf:b7211155
2025-03-25 11:23:36
Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la [guía de MiniBolt](https://minbolt.info/).
Esto tiene una **razón**, por supuesto una **solución**, además de una **conclusión**. Sin entrar en demasiados detalles:
## La razón
El **bloqueo a Cloudflare**, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una [orden judicial](https://www.poderjudicial.es/search/AN/openDocument/3c85bed480cbb1daa0a8778d75e36f0d/20221004) emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización.
Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo [ECH](https://developers.cloudflare.com/ssl/edge-certificates/ech) (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar **bloqueos basados en dominios**, lo que les obliga a recurrir a **bloqueos más amplios por IP o rangos de IP** para cumplir con la orden judicial.
Esta práctica tiene **consecuencias graves**, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un **perjuicio para terceros**, **restringiendo el acceso a muchos dominios legítimos** que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la [web de MiniBolt](https://minibolt.minibolt.info) y su dominio `minibolt.info`, los cuales **utilizan Cloudflare como proxy** para aprovechar las medidas de **seguridad, privacidad, optimización y servicios** adicionales que la plataforma ofrece de forma gratuita.
Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.

## La solución
Obviamente, **MiniBolt no dejará de usar Cloudflare** como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para **evitar esta restricción** y poder acceder:
**~>** Utiliza **una VPN**:
Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad:
- [IVPN](https://www.ivpn.net/es/)
- [Mullvad VPN](https://mullvad.net/es/vpn)
- [Proton VPN](https://protonvpn.com/es-es) (**gratis**)
- [Obscura VPN](https://obscura.net/) (**solo para macOS**)
- [Cloudfare WARP](https://developers.cloudflare.com/cloudflare-one/connections/connect-devices/warp/download-warp/) (**gratis**) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos:
1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy"
2. Marca la casilla "Habilite el modo proxy en este dispositivo"
3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias
4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio.
3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a [esta](https://minibolt.minibolt.info/system/system/privacy#example-from-firefox) para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la [guía de MiniBolt](https://minibolt.minibolt.info/) sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info [AQUÍ](https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958).

**~>** [**Proxifica tu navegador para usar la red de Tor**](https://minibolt.minibolt.info/system/system/privacy#ssh-remote-access-through-tor), o utiliza el [**navegador oficial de Tor**](https://www.torproject.org/es/download/) (recomendado).

## La conclusión
Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la [Declaración de Independencia del Ciberespacio](https://es.wikisource.org/wiki/Declaraci%C3%B3n_de_independencia_del_ciberespacio) que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad.
Es momento de actuar y estar preparados: debemos **impulsar el desarrollo y la difusión** de las **herramientas anticensura** que tenemos a nuestro alcance, protegiendo así la **libertad digital** y asegurando un acceso equitativo a la información para todos
Este compromiso es uno de los **pilares fundamentales de MiniBolt,** lo que convierte este desafío en una oportunidad para poner a prueba las **soluciones anticensura** [ya disponibles](https://minibolt.minibolt.info/bonus-guides/system/tor-services), así como **las que están en camino**.
¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!

---
Fuentes:
* https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239
* https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257
* https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958
* https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689
* https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007
-

@ 3b7fc823:e194354f
2025-03-23 03:54:16
A quick guide for the less than technical savvy to set up their very own free private tor enabled email using Onionmail. Privacy is for everyone, not just the super cyber nerds.
Onion Mail is an anonymous POP3/SMTP email server program hosted by various people on the internet. You can visit this site and read the details: https://en.onionmail.info/
1. Download Tor Browser
First, if you don't already, go download Tor Browser. You are going to need it. https://www.torproject.org/
2. Sign Up
Using Tor browser go to the directory page (https://onionmail.info/directory.html) choose one of the servers and sign up for an account. I say sign up but it is just choosing a user name you want to go before the @xyz.onion email address and solving a captcha.
3. Account information
Once you are done signing up an Account information page will pop up. **MAKE SURE YOU SAVE THIS!!!** It has your address and passwords (for sending and receiving email) that you will need. If you lose them then you are shit out of luck.
4. Install an Email Client
You can use Claws Mail, Neomutt, or whatever, but for this example, we will be using Thunderbird.
a. Download Thunderbird email client
b. The easy setup popup page that wants your name, email, and password isn't going to like your user@xyz.onion address. Just enter something that looks like a regular email address such as name@example.com and the **Configure Manually**option will appear below. Click that.
5. Configure Incoming (POP3) Server
Under Incoming Server:
Protocol: POP3
Server or Hostname: xyz.onion (whatever your account info says)
Port: 110
Security: STARTTLS
Authentication: Normal password
Username: (your username)
Password: (POP3 password).
6. Configure Outgoing (SMTP) Server
Under Outgoing Server:
Server or Hostname: xyz.onion (whatever your account info says)
Port: 25
Security: STARTTLS
Authentication: Normal password
Username: (your username)
Password: (SMTP password).
7. Click on email at the top and change your address if you had to use a spoof one to get the configure manually to pop up.
8. Configure Proxy
a. Click the **gear icon** on the bottom left for settings. Scroll all the way down to **Network & Disk Space**. Click the **settings button** next to **Connection. Configure how Thunderbird connects to the internet**.
b. Select **Manual Proxy Configuration**. For **SOCKS Host** enter **127.0.0.1** and enter port **9050**. (if you are running this through a VM the port may be different)
c. Now check the box for **SOCKS5** and then **Proxy DNS when using SOCKS5** down at the bottom. Click OK
9. Check Email
For thunderbird to reach the onion mail server it has to be connected to tor. Depending on your local setup, it might be fine as is or you might have to have tor browser open in the background. Click on **inbox** and then the **little cloud icon** with the down arrow to check mail.
10. Security Exception
Thunderbird is not going to like that the onion mail server security certificate is self signed. A popup **Add Security Exception** will appear. Click **Confirm Security Exception**.
You are done. Enjoy your new private email service.
**REMEMBER: The server can read your emails unless they are encrypted. Go into account settings. Look down and click End-toEnd Encryption. Then add your OpenPGP key or open your OpenPGP Key Manager (you might have to download one if you don't already have one) and generate a new key for this account.**
-

@ 21335073:a244b1ad
2025-03-18 20:47:50
**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.**
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
**Course:**
- The creation of the internet and computers
- The fight for cryptography
- The tech supply chain from the ground up (example: human rights violations in the supply chain)
- Corporate tech
- Freedom tech
- Data privacy
- Digital privacy rights
- AI (history-current)
- Online safety (predators, scams, catfishing, extortion)
- Bitcoin
- Laws
- How to deal with online hate and harassment
- Information on who to contact if you are being abused online or offline
- Algorithms
- How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-

@ 21335073:a244b1ad
2025-03-18 14:43:08
**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.**
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
**Course:**
- The creation of the internet and computers
- The fight for cryptography
- The tech supply chain from the ground up (example: human rights violations in the supply chain)
- Corporate tech
- Freedom tech
- Data privacy
- Digital privacy rights
- AI (history-current)
- Online safety (predators, scams, catfishing, extortion)
- Bitcoin
- Laws
- How to deal with online hate and harassment
- Information on who to contact if you are being abused online or offline
- Algorithms
- How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-

@ a07fae46:7d83df92
2025-03-18 12:31:40
if the JFK documents come out and are nothing but old hat, it will be disappointing. but if they contain revelations, then they are an unalloyed good. unprecedented and extraordinary; worthy of praise and admiration. they murdered the president in broad daylight and kept 80,000 related documents secret for 60 years. the apparatus that did that and got away with it, is 100+ years in the making. the magic bullet was just the starting pistol of a new *era*; a *level up* in an [old game](https://archive.org/details/TragedyAndHope_501/page/n5/mode/2up?q=feudalist+fashion). it won't be dismantled and your republic delivered back with a bow in *2 months*. have a little humility and a little gratitude. cynicism is easy. it's peak mid-wittery. yeah no shit everything is corrupt and everyone's likely captured by [AIPAC](https://books.google.com/books/publisher/content?id=gKVKDwAAQBAJ&pg=PT68&img=1&zoom=3&hl=en&bul=1&sig=ACfU3U2pagVXTYdJOKxkAwmmFQpuSnoS5g&w=1280) or something beyond. YOU THINK AIPAC is the [ALL SEEING EYE](https://archive.org/details/the-all-seeing-eye-vol-1-5-manly-p.-hall-may-1923-sept-1931)?
you can keep going, if you want to, but have some awareness and appreciation for where we are and what it took to get here. the first 'you are fake news' was also a shot heard 'round the world and you are riding high on it's [Infrasound](https://en.wikipedia.org/wiki/Infrasound) wave, still reverberating; unappreciative of the profound delta in public awareness and understanding, and rate of change, that has occurred since that moment, in [2017](https://www.youtube.com/watch?v=Vqpzk-qGxMU). think about where we were back then, especially with corporate capture of the narrative. trump's bullheaded behavior, if only ego-driven, *is* what broke the spell. an *actual* moment of savage bravery is what allows for your current jaded affectation. black pilled is boring. it's intellectually lazy. it is low-resolution-thinking, no better than progressives who explain the myriad ills of the world through 'racism'. normalcy bias works both ways. i'm not grading you on a curve that includes NPCs. i'm grading you against those of us with a mind, on up. do better.
the best Webb-style doomer argument is essentially 'the mouse trap needs a piece of cheese in order to work'. ok, but it doesn't need 3 pieces of cheese, or 5. was FreeRoss the piece of cheese? was the SBR the cheese? real bitcoiners know how dumb the 'sbr is an attempt to takeover btc' narrative is, so extrapolate from that. what about withdrawal from the WHO? freeze and review of USAID et al? how many pieces of cheese before we realize it's not a trap? it's just a messy endeavor.
Good morning.
#jfkFiles #nostrOnly
-

@ bc52210b:20bfc6de
2025-03-14 20:39:20
When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract.
The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable.
In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions.
Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure.
-

@ df173277:4ec96708
2025-02-07 00:41:34
## **Building Our Confidential Backend on Secure Enclaves**
With our newly released [private and confidential **Maple AI**](https://trymaple.ai/?ref=blog.opensecret.cloud) and the open sourcing of our [**OpenSecret** platform](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud) code, I'm excited to present this technical primer on how we built our confidential compute platform leveraging **secure enclaves**. By combining AWS Nitro enclaves with end-to-end encryption and reproducible builds, our platform gives developers and end users the confidence that user data is protected, even at runtime, and that the code operating on their data has not been tampered with.
## **Auth and Databases Today**
As developers, we live in an era where protecting user data means "encryption at rest," plus some access policies and procedures. Developers typically run servers that:
1. Need to register users (authentication).
2. Collect and process user data in business-specific ways, often on the backend.
Even if data is encrypted at rest, it's commonly unlocked with a single master key or credentials the server holds. This means that data is visible during runtime to the application, system administrators, and potentially to the hosting providers. This scenario makes it difficult (or impossible) to guarantee that sensitive data isn't snooped on, memory-dumped, or used in unauthorized ways (for instance, training AI models behind the scenes).
## **"Just Trust Us" Isn't Good Enough**
In a traditional server architecture, users have to take it on faith that the code handling their data is the same code the operator claims to be running. Behind the scenes, applications can be modified or augmented to forward private information elsewhere, and there is no transparent way for users to verify otherwise. This lack of proof is unsettling, especially for services that process or store highly confidential data.
Administrators, developers, or cloud providers with privileged access can inspect memory in plaintext, attach debuggers, or gain complete visibility into stored information. Hackers who compromise these privileged levels can directly access sensitive data. Even with strict policies or promises of good conduct, the reality is that technical capabilities and misconfigurations can override words on paper. If a server master key can decrypt your data or can be accessed by an insider with root permissions, then "just trust us" loses much of its credibility.
The rise of AI platforms amplifies this dilemma. User data, often full of personal details, gets funneled into large-scale models that might be training or fine-tuning behind the scenes. Relying on vague assurances that "we don't look at your data" is no longer enough to prevent legitimate concerns about privacy and misuse. Now more than ever, providing a **strong, verifiable** guarantee that data remains off-limits, even when actively processed, has become a non-negotiable requirement for trustworthy services.
## **Current Attempts at Securing Data**
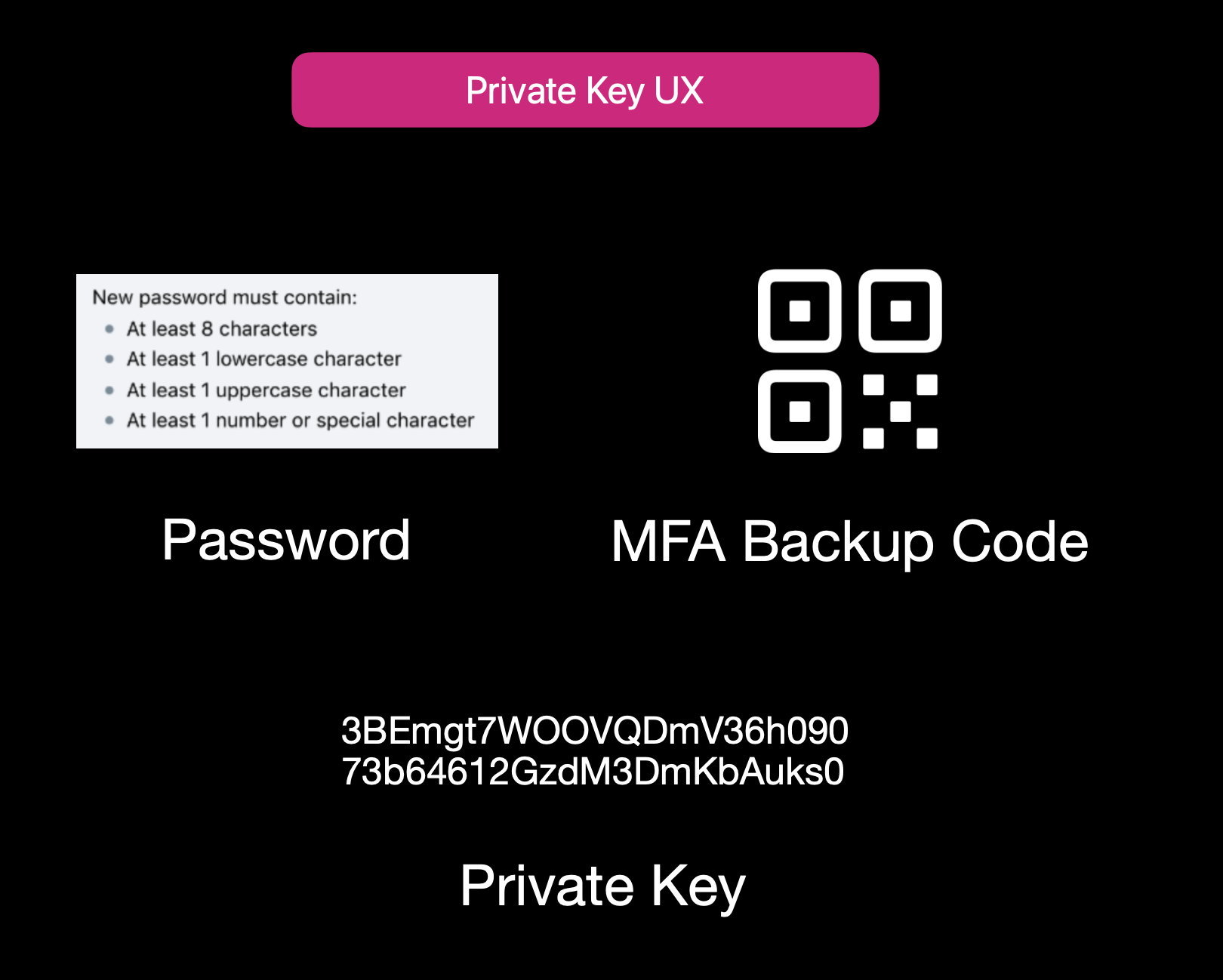Current User Experience of E2EE Apps
While properly securing data is not easy, it isn't to say that no one is trying. Some solutions use **end-to-end encryption** (E2EE), where user data is encrypted client-side with a password or passphrase, so not even the server operator can decrypt it. That approach can be quite secure, but it also has its **limitations**:
1. **Key Management Nightmares**: If a user forgets their passphrase, the data is effectively lost, and there's no way to recover it from the developer's side.
2. **Feature Limitations**: Complex server-side operations (like offline/background tasks, AI queries, real-time collaboration, or heavy computation) can't easily happen if the server is never capable of processing decrypted data.
3. **Platform Silos**: Some solutions rely on iCloud, Google Drive, or local device storage. That can hamper multi-device usage or multi-OS compatibility.
Other approaches include self-hosting. However, these either burden users with dev ops overhead or revert to the "trust me" model for the server if you "self-host" on a cloud provider.
## **Secure Enclaves**
### **The Hybrid Approach**
Secure enclaves offer a compelling middle ground. They combine the privacy benefits of keeping data secure from prying admins while still allowing meaningful server-side computation. In a nutshell, an enclave is a protected environment within a machine, isolated at the hardware level, so that even if the OS or server is compromised, the data and code inside the enclave remain hidden.
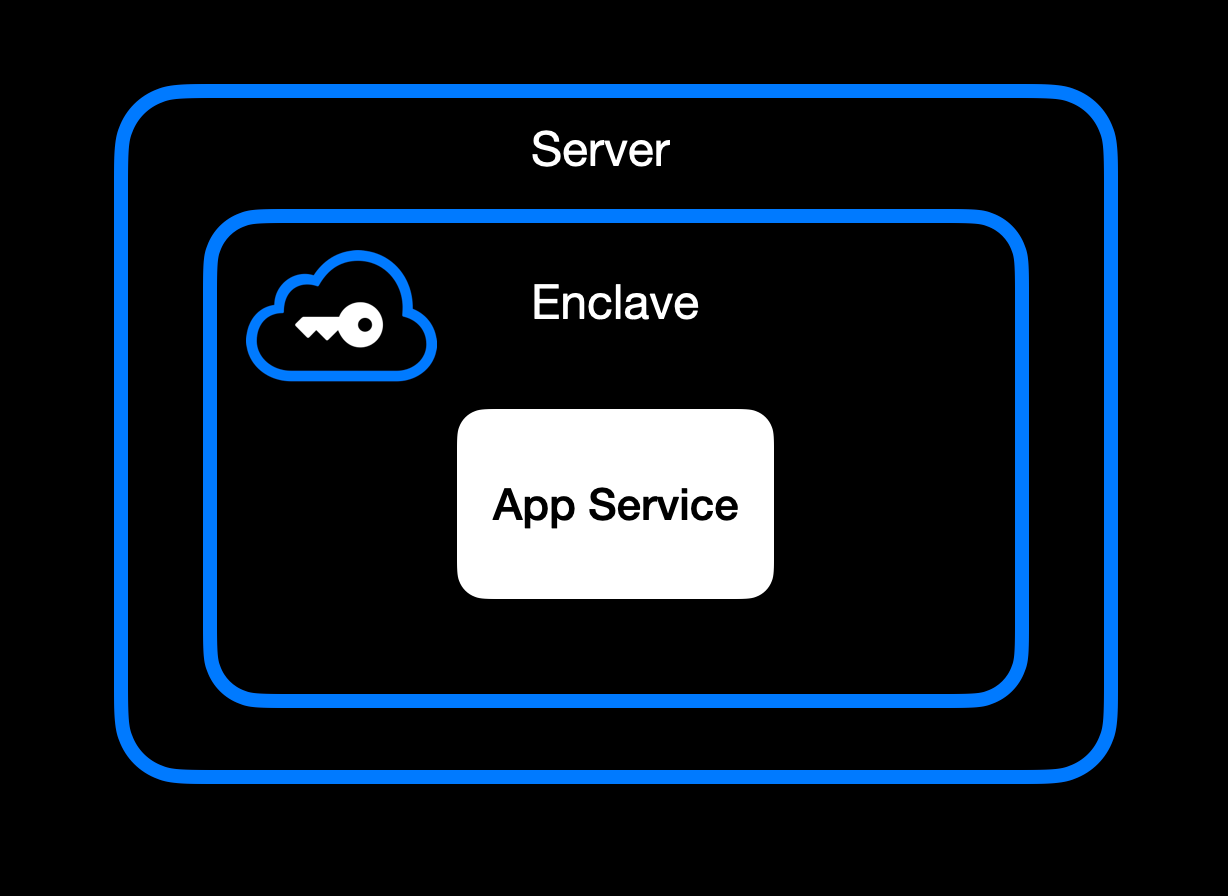App Service Running Inside Secure Enclave
### **High-Level Goal of Enclaves**
Enclaves, also known under the broader umbrella of **confidential computing**, aim to:\
• **Lock down data** so that only authorized code within the enclave can process the original plaintext data.\
• **Deny external inspection** by memory dumping, attaching a debugger, or intercepting plaintext network traffic.\
• **Prove** to external users or services that an enclave is running unmodified, approved code (this is where **remote attestation** comes in).
### **Different Secure Enclave Solutions**
[**AMD SEV**](https://www.amd.com/en/developer/sev.html?ref=blog.opensecret.cloud) **(Secure Encrypted Virtualization)** encrypts an entire virtual machine's memory so that even a compromised hypervisor cannot inspect or modify guest data. Its core concept is "lift-and-shift" security. No application refactoring is required because hardware-based encryption automatically protects the OS and all VM applications. Later enhancements (SEV-ES and SEV-SNP) added encryption of CPU register states and memory integrity protections, further limiting hypervisor tampering. This broad coverage means the guest OS is included in the trusted boundary. AMD SEV has matured into a robust solution for confidential VMs in multi-tenant clouds.
[**Intel TDX**](https://www.intel.com/content/www/us/en/developer/tools/trust-domain-extensions/overview.html?ref=blog.opensecret.cloud) **(Trust Domain Extensions)** shifts from process-level enclaves to full VM encryption, allowing an entire guest operating system and its applications to run in an isolated "trust domain." Like AMD SEV, Intel TDX encrypts and protects all memory the VM uses from hypervisors or other privileged software, so developers do not need to refactor their code to benefit from hardware-based confidentiality. This broader scope addresses many SGX limitations, such as strict memory bounds and the need to split out enclave-specific logic, and offers a more straightforward "lift-and-shift" path for running existing workloads privately. While SGX is now deprecated, TDX carries forward the core confidential computing principles but applies them at the virtual machine level for more substantial isolation, easier deployment, and the ability to scale up to large, memory-intensive applications.
[**Apple Secure Enclave and Private Compute**](https://security.apple.com/blog/private-cloud-compute/?ref=blog.opensecret.cloud) is a dedicated security coprocessor embedded in most Apple devices (iPhones, iPads, Macs) and now extended to Apple's server-side AI infrastructure. It runs its own microkernel, has hardware-protected memory, and securely manages operations such as biometric authentication, key storage, and cryptographic tasks. Apple's "Private Compute" approach in the cloud brings similar enclave capabilities to server-based AI, enabling on-device-grade privacy even when requests are processed in Apple's data centers.
[**AWS Nitro Enclaves**](https://docs.aws.amazon.com/enclaves/latest/user/nitro-enclave.html?ref=blog.opensecret.cloud) carve out a tightly isolated "mini-VM" from a parent EC2 instance, with its own vCPUs and memory guarded by dedicated Nitro cards. The enclave has no persistent storage and no external network access, significantly reducing the attack surface. Communication with the parent instance occurs over a secure local channel (vsock), and AWS offers hardware-based attestation so that secrets (e.g., encryption keys from AWS KMS) can be accessed only to the correct enclave. This design helps developers protect sensitive data or code even if the main EC2 instance's OS is compromised.
[**NVIDIA GPU TEEs**](https://www.nvidia.com/en-us/data-center/solutions/confidential-computing/?ref=blog.opensecret.cloud) **(Hopper H100 and Blackwell)** extend confidential computing to accelerated workloads by encrypting data in GPU memory and ensuring that even a privileged host cannot view or tamper with it. Data moving between CPU and GPU is encrypted in transit, so sensitive model weights or inputs remain protected during AI training or inference. NVIDIA's hardware and drivers handle secure data paths under the hood, allowing confidential large language model (LLM) workloads and other GPU-accelerated computations to run with minimal performance overhead and strong security guarantees.
### **Key Benefits**
One major advantage of enclaves is their ability to **keep memory completely off-limits** to outside prying eyes. Even administrators who can normally inspect processes at will are blocked from peeking into the enclave's protected memory space. The enclave model is a huge shift in the security model: it prevents casual inspection and defends against sophisticated memory dumping techniques that might otherwise leak secrets or sensitive data.
Another key benefit centers on cryptographic keys that are **never exposed outside the enclave**. Only verified code running inside the enclave environment can run decryption or signing operations, and it can only do so while that specific code is running. This ensures that compromised hosts or rogue processes, even those with high-level privileges, are unable to intercept or misuse the keys because the keys remain strictly within the trusted boundary of the hardware.
Enclaves can also offer the power of **remote attestation**, allowing external clients or systems to confirm that they're speaking to an authentic, untampered enclave. By validating the hardware's integrity measurements and enclave-specific proofs, the remote party can be confident in the underlying security properties, an important guarantee in multi-tenant environments or whenever trust boundaries extend across different organizations and networks.
Beyond that, **reproducible builds** can create a verifiable fingerprint proving which binary runs in the enclave. This is a step above a simple "trust us" approach. Anyone can independently recreate the enclave image and verify the resulting cryptographic hash by using a reproducible build system (for example, [our NixOS-based solution](https://github.com/OpenSecretCloud/opensecret/blob/master/flake.nix?ref=blog.opensecret.cloud)). If it matches, then users and developers know precisely how code handles their data, boosting confidence that no hidden changes exist.
It's worth noting that although enclaves shield you from software devs, cloud providers, and insider threats, you do have to trust the **hardware vendor** (Intel, AMD, Apple, AWS, or NVIDIA) to implement their microcode and firmware securely. The entire enclave model could be theoretically undermined if a CPU maker's root keys or manufacturing process were compromised. Fortunately, these companies undergo extensive audits and firmware validations (often with third-party researchers), and their remote attestation mechanisms allow you to confirm specific firmware versions before trusting an enclave. While this adds a layer of "vendor trust," it's still a far more contained risk than trusting an entire operating system or cloud stack, so enclaves remain a strong step forward in practical, confidential computing.
## **How We Use Secure Enclaves**
Now that we've covered the general idea of enclaves let's look at how we specifically implement them in OpenSecret, our developer platform for handling user auth, private keys, data encryption, and AI workloads.
### **Our Stack: AWS Nitro + Nvidia TEE**
• **AWS Nitro Enclaves for the backend**: All critical logic, authentication, private key management, and data encryption/decryption run inside an AWS Nitro Enclave.
• **Nvidia Trusted Execution for AI**: For large AI inference (such as the Llama 3.3 70B model), we utilize Nvidia's GPU-based TEEs to protect even GPU memory. This means users can feed sensitive data to the AI model **without** exposing it in plaintext to the GPU providers or us as the operator. [Edgeless Systems](https://www.edgeless.systems/?ref=blog.opensecret.cloud) is our Nvidia TEE provider, and due to the power of enclave verification, we don't need to worry about who runs the GPUs. We know requests can't be inspected or tampered with.
### **End-to-End Encryption from Client to Enclave**
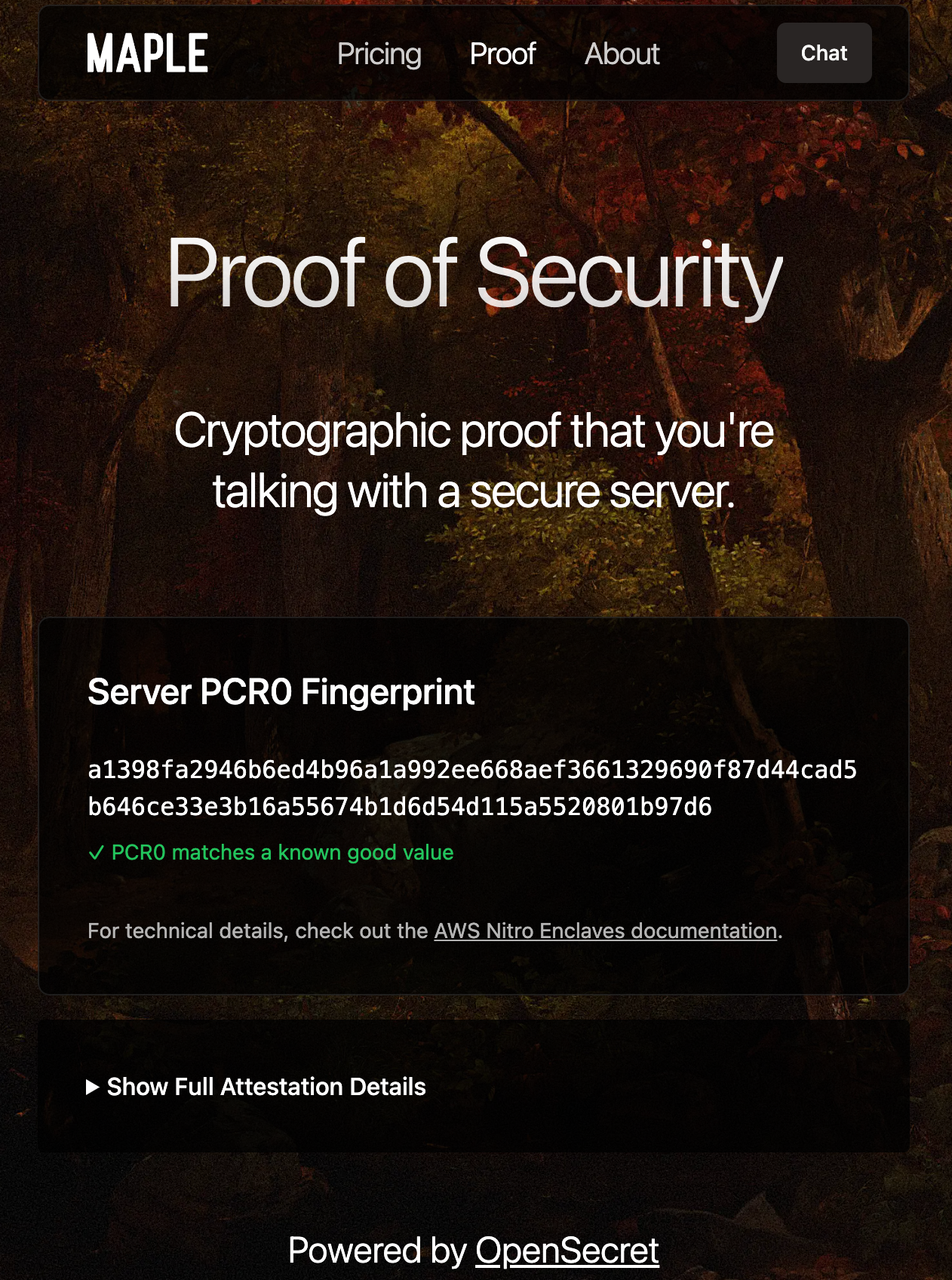Client-side Enclave Attestation from Maple AI
Before login or data upload, the user/client verifies the **enclave attestation** from our platform. This process proves that the specific Nitro Enclave is genuine and runs the exact code we've published. You can check this out live on [Maple AI's attestation page](https://trymaple.ai/proof?ref=blog.opensecret.cloud).
Based on the attestation, the client establishes a secure ephemeral communication channel that only that enclave can decrypt. While we take advantage of SSL, it is typically not terminated inside the enclave itself. To ensure there's full encrypted data transfer all the way through to the enclave, we establish this additional handshake based on the attestation document that is used for all API requests during the client session.
From there, the user's credentials, private keys, and data pass through this secure channel directly into the enclave, where they are decrypted and processed according to the user's request.
### **In-Enclave Operations**
At the core of OpenSecret's approach is the conviction that security-critical tasks must happen inside the enclave, where even administrative privileges or hypervisor-level compromise cannot expose plaintext data. This encompasses everything from when a user logs in to creating and managing sensitive cryptographic keys. By confining these operations to a protected hardware boundary, developers can focus on building their applications without worrying about accidental data leaks, insider threats, or malicious attempts to harvest credentials. The enclave becomes the ultimate gatekeeper: it controls how data flows and ensures that nothing escapes in plain form.
User Auth Methods running inside Enclave
A primary example is **user authentication**. All sign-in workflows, including email/password, OAuth, and upcoming passkey-based methods, are handled entirely within the enclave. As soon as a user's credentials enter our platform through the encrypted channel, they are routed straight into the protected environment, bypassing the host's operating system or any potential snooping channels. From there, authentication and session details remain in the enclave, ensuring that privileged outsiders cannot intercept or modify them. By centralizing these identity flows within a sealed environment, developers can assure their users that no one outside the enclave (including the cloud provider or the app's own sysadmins) can peek at, tamper with, or access sensitive login information.
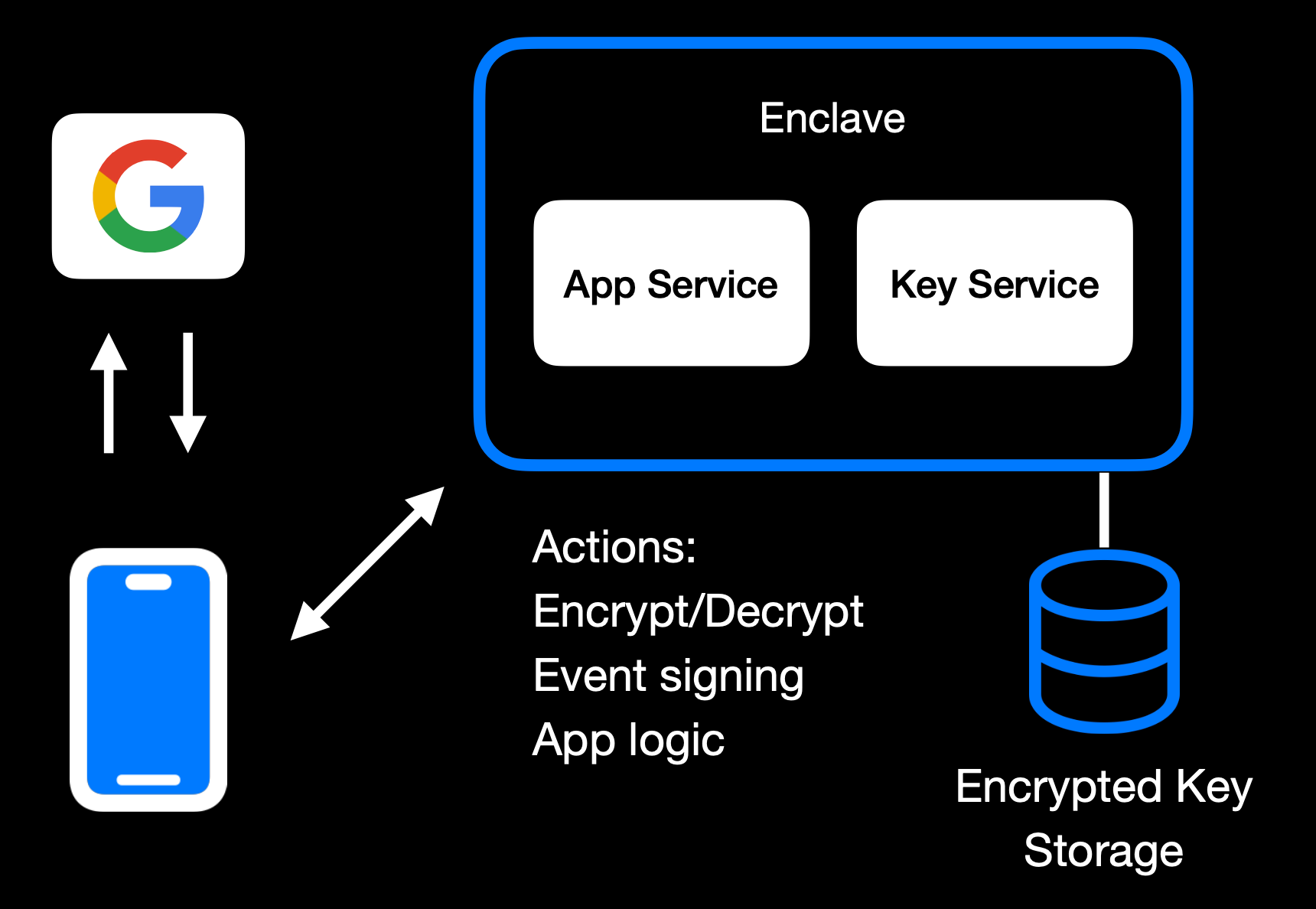Main Enclave Operations in OpenSecret
The same principle applies to **private key management**. Whether keys are created fresh in the enclave or securely transferred into it, they remain sealed away from the rest of the system. Operations like digital signing or content decryption happen only within the hardware boundary, so raw keys never appear in any log, file system, or memory space outside the enclave. Developers retain the functionality they need, such as verifying user actions, encrypting data, or enabling secure transactions without ever exposing keys to a broader (and more vulnerable) attack surface. User backup options exist as well, where the keys can be securely passed to the end user.
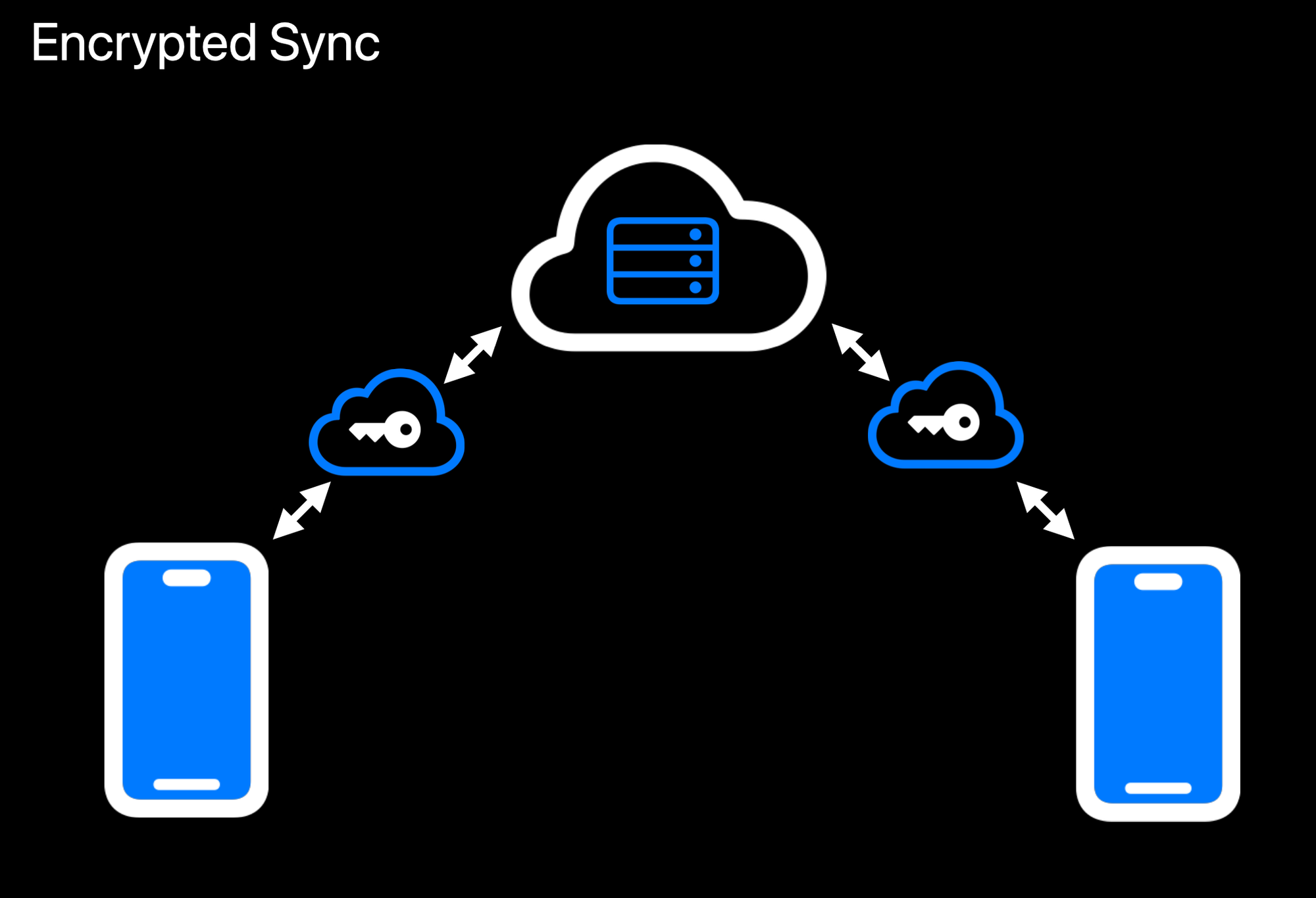Realtime Encrypted Data Sync on Multiple Devices
Another crucial aspect is **data encryption at rest**. While user data ultimately needs to be stored somewhere outside the enclave, the unencrypted form of that data only exists transiently inside the protected environment. Encryption and decryption routines run within the enclave, which holds the encryption keys strictly in memory under hardware guards. If a user uploads data, it is promptly secured before it leaves the enclave. When data is retrieved, it remains encrypted until it reenters the protected region and is passed back to the user through the secured communication channel. This ensures that even if someone gains access to the underlying storage or intercepts data in transit, they will see only meaningless ciphertext.
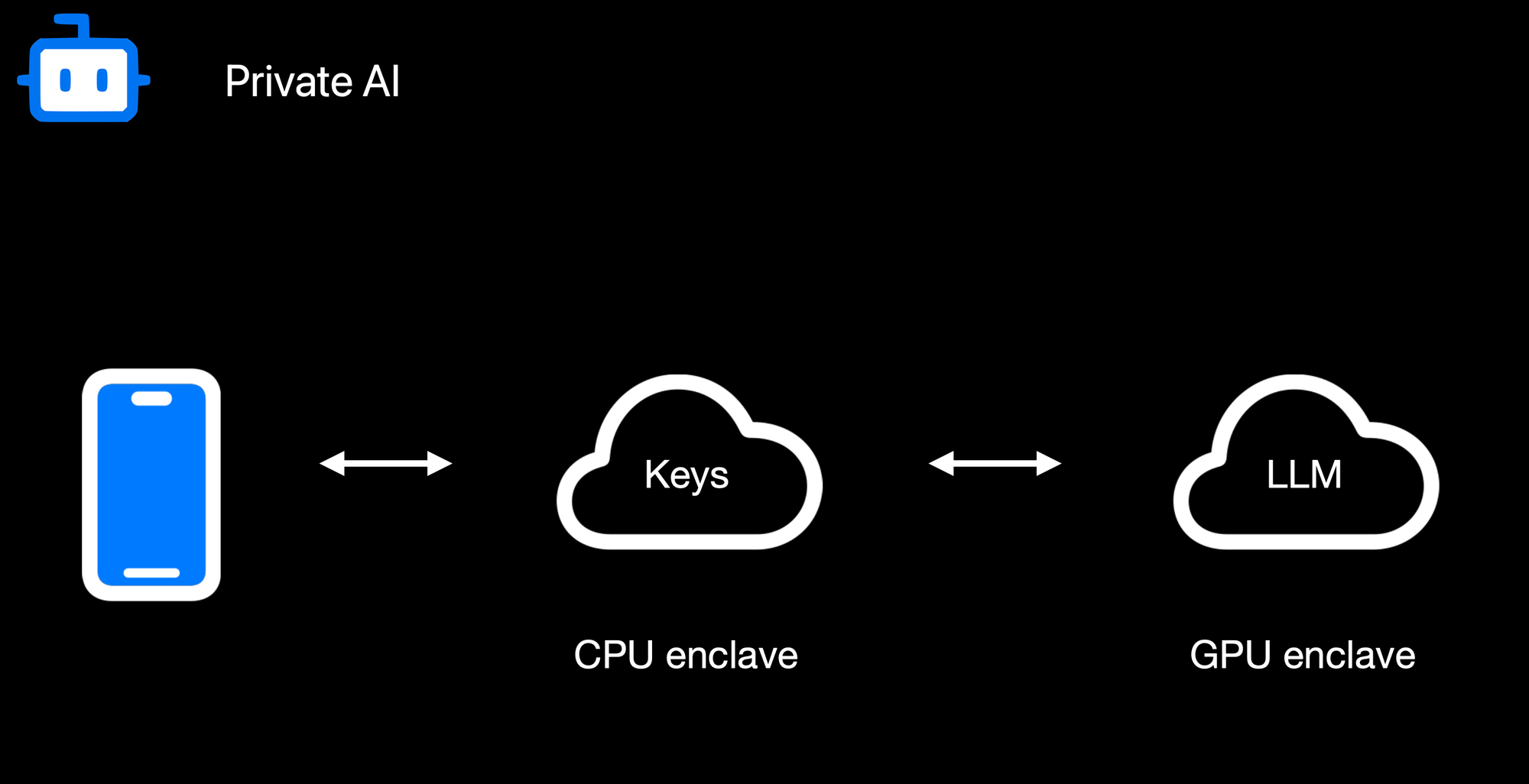Confidential AI Workloads
Finally, **confidential AI workloads** build upon this same pattern: the Nitro enclave re-encrypts data so it can be processed inside a GPU-based trusted execution environment (TEE) for inference or other advanced computations. Sensitive data, like user-generated text or private documents, never appears in the clear on the host or within GPU memory outside the TEE boundary. When an AI process finishes, only the results are returned to the enclave, which can then relay them securely to the requesting user. By seamlessly chaining enclaves together, from CPU-based Nitro Enclaves to GPU-accelerated TEEs, we can deliver robust, hardware-enforced privacy for virtually any type of server-side or AI-driven operation.
### **Reproducible Builds + Verification**
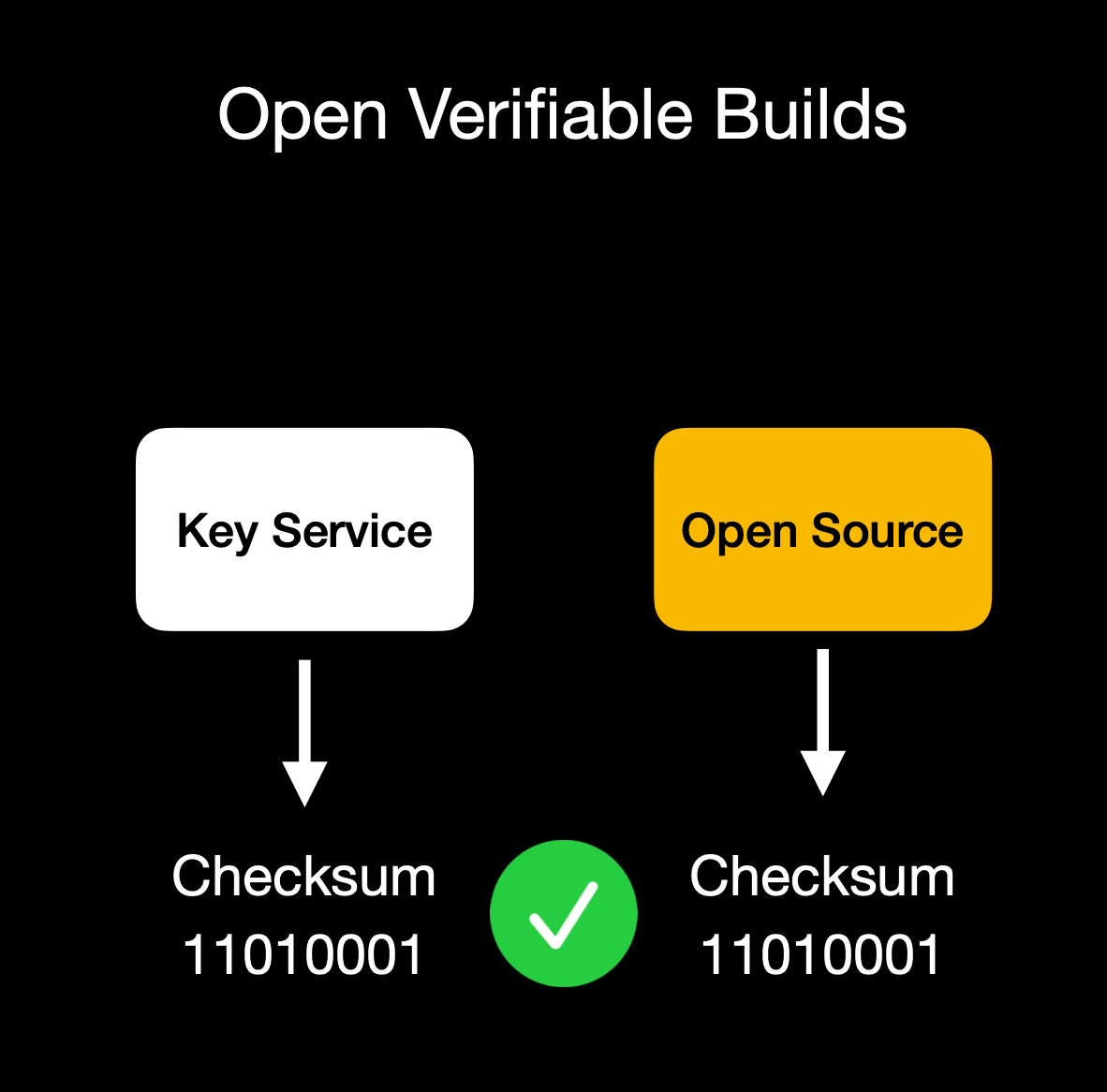Client verifies enclave attestation document
We build our enclaves on **NixOS** with reproducible builds, ensuring that anyone can verify that the binary we publish is indeed the binary running in the enclave. This build process is essential for proving we haven't snuck in malicious code to exfiltrate data or collect sensitive logs.
Our code is fully open source ([GitHub: OpenSecret](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud)), so you can audit or run it yourself. You can also verify that the cryptographic measurement the build process outputs matches the measurement reported by the enclave during attestation.
## **Putting It All Together**
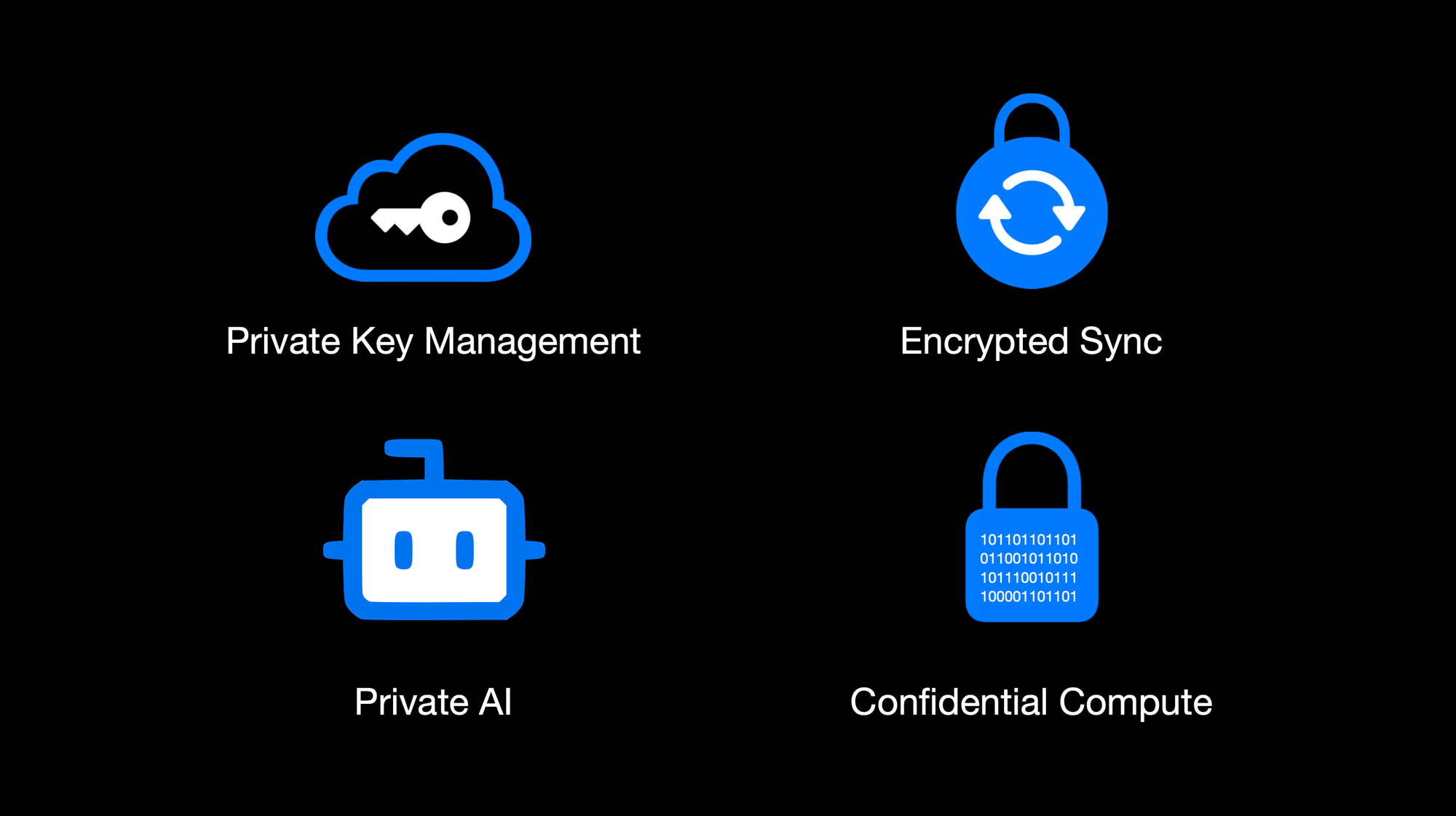OpenSecret Offering: Private Key Management, Encrypted Sync, Private AI, and Confidential Compute
By weaving secure enclaves into every step, from authentication to data handling to AI inference, we shift the burden of trust away from human policies and onto provable, hardware-based protections. For app developers, you can offer your users robust privacy guarantees without rewriting all your business logic or building an entire security stack from scratch. Whether you're storing user credentials or running complex operations on sensitive data, the enclave approach ensures plaintext remains inaccessible to even the most privileged parties outside the enclave boundary. Developers can focus on building great apps, while OpenSecret handles the cryptographic "lock and key" behind the scenes.
This model provides a secure-by-design environment for industries that demand strict data confidentiality, such as healthcare, fintech, cryptocurrency apps for secure key management, or decentralized identity platforms. Instead of worrying about memory dumps or backend tampering, you can trust that once data enters the enclave, it's sealed off from unauthorized eyes, including from the app developers themselves. And these safeguards don't just apply to niche use cases. Even general-purpose applications that handle login flows and user-generated content stand to benefit, especially as regulatory scrutiny grows around data privacy and insider threats.
Imagine a telehealth startup using OpenSecret enclaves to protect patient information for remote consultations. Not only would patient data remain encrypted at rest, but any AI-driven analytics to assist with diagnoses could be run privately within the enclave, ensuring no one outside the hardware boundary can peek at sensitive health records. A fintech company could similarly isolate confidential financial transactions, preventing even privileged insiders from viewing or tampering with raw transaction details. These real-world implementations give developers a clear path to adopting enclaves for serious privacy and compliance needs without overhauling their infrastructure.
OpenSecret aims to be a **full developer platform** with end-to-end security from day one. By incorporating user authentication, data storage, and GPU-based confidential AI into a single service, we eliminate many of the traditional hurdles in adopting enclaves. No more juggling separate tools for cryptographic key management, compliance controls, and runtime privacy. Instead, you get a unified stack that keeps data encrypted in transit, at rest, and in use.
Our solution also caters to the exploding demand for AI applications: with TEE-enabled GPU workloads, you can securely process sensitive data for text inference without ever exposing raw plaintext or sensitive documents to the host system.
The result is a new generation of apps that deliver advanced functionality, like real-time encrypted data sync or AI-driven insights, while preserving user privacy and meeting strict regulatory requirements. You don't have to rely on empty "trust us" promises because hardware enclaves, remote attestation, and reproducible builds collectively guarantee the code is running untampered. In short, OpenSecret offers the building blocks needed to create truly confidential services and experiences, allowing you to innovate while ensuring data protection remains ironclad.
## **Things to Come**
We're excited to build on our enclaved approach. Here's what's on our roadmap:
• **Production Launch**: We're using this in production now with [Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud) and have a developer preview playground up and running. We'll have the developer environment ready for production in a few months.\
• **Multi-Tenant Support**: Our platform currently works for single tenants, but we're opening this up so developers can onboard without needing a dedicated instance.\
• **Self-Serve Frontend**: A dev-friendly portal for provisioning apps, connecting OAuth or email providers, and managing users.\
• **External Key Signing Options**: Integrations with custom hardware security modules (HSMs) or customer-ran key managers that can only process data upon verifying the enclave attestation.\
• **Confidential Computing as a Service**: We'll expand our platform so that other developers can quickly create enclaves for specialized workloads without dealing with the complexities of Nitro or GPU TEEs.\
• **Additional SDKs**: In addition to our [JavaScript client-side SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud), we plan to launch official support for Rust, Python, Swift, Java, Go, and more.\
• **AI API Proxy with Attestation/Encryption**: We already provide an easy way to [access a Private AI through Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud), but we'd like to open this up more for existing tools and developers. We'll provide a proxy server that users can run on their local machines or servers that properly handle encryption to our OpenAI-compatible API.
## **Getting Started**
Ready to see enclaves in action? Here's how to dive in:\
1. **Run OpenSecret**: Check out our open-source repository at [OpenSecret on GitHub](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud). You can run your own enclaved environment or try it out locally with Docker.\
2. **Review Our SDK**: Our [JavaScript client SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud) makes it easy to handle sign-ins, put/get encrypted data, sign with user private keys, etc. It handles attestation verification and encryption under the hood, making the API integration seamless.\
3. **Play with Maple AI**: Try out [Maple AI](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) as an example of an AI app built directly on OpenSecret. Your queries are encrypted end to end, and the Llama model sees them only inside the TEE.\
4. **Developer Preview**: Contact us if you want an invite to our early dev platform. We'll guide you through our SDK and give you access to the preview server. We'd love to build with you and incorporate your feedback as we develop this further.
## **Conclusion**
By merging secure enclaves (AWS Nitro and Nvidia GPU TEEs), user authentication, private key management, and an end-to-end verifiable encrypted approach, **OpenSecret** provides a powerful platform where we protect user data during collection, storage, and processing. Whether it's for standard user management, handling private cryptographic keys, or powering AI inference, the technology ensures that **no one**, not even us or the cloud provider, can snoop on data in use.
**We believe** this is the future of trustworthy computing in the cloud. And it's **all open source**, so you don't have to just take our word for it: you can see and verify everything yourself.
Do you have questions, feedback, or a use case you'd like to test out? Come join us on [GitHub](https://github.com/OpenSecretCloud?ref=blog.opensecret.cloud), [Discord](https://discord.gg/ch2gjZAMGy?ref=blog.opensecret.cloud), or email us for a developer preview. We can't wait to see what you build!
*Thank you for reading, and welcome to the era of enclaved computing.*
-

@ 04cb16e4:2ec3e5d5
2025-04-02 10:51:31
Wenn irgendein weltpolitisches Thema auf den Tisch kommt, wird zumeist erst einmal gefragt, ob du dafür oder dagegen bist und auf welcher Seite du dich befindest. Das macht es einfacher, dich als Freund oder Feind einzusortieren. So wird das Leben übersichtlicher und man muss nicht in die Tiefe gehen und sich mit lästigen Details auseinandersetzen. Man muss auch nicht verreisen um sich ein Bild zu machen. Dafür gibt es ja die Tagesschau. Klassisches Beispiel: Ich war vor Kurzem mit einigen Freunden essen. Einer berichtete entsetzt: „Der Putin hat die Heimatstadt von Selenski angegriffen!“
 Ich versuchte mir das bildlich vorzustellen und kam zu dem Schluss, das „der Putin“ wahrscheinlich Verstärkung dabei hatte. Und ausgerechnet nachdem Trump und dessen Flügelmann Vance den armen Wolodymyr rund gemacht hatten, greift der böse Imperator dessen Heimatstadt an. Das ist fies! Das macht „der Putin“ wahrscheinlich immer so, wenn er jemandem eins auswischen will. Die Heimatstadt angreifen! Ganz gleich, ob es strategisch gerade Sinn macht oder nicht. "Der Putin" ist halt ein Teufel.
[Telegramkanal RBM](https://t.me/radio_berliner_morgenroete_de)
[Radio Berliner Morgenröte auf X](https://x.com/RBM_Schindler)
Ich denke viele gucken einfach zu viele qualitativ minderwertige Spielfilme und können Fiktion und Realität nicht mehr voneinander unterscheiden. Möglicherweise meinen sie auch, weil sie die Handlung eines Kriegsfilmes gerafft haben, verstehen sie einen Krieg.
<https://www.eisbrenner.de/produkt-kategorie/buch/>
<https://befreiung.org/>
Mein Gesprächspartner Tino Eisbrenner hat keine Sightseeing Tour durch Moskau gemacht, sondern ist in Land und Leute regelrecht eingetaucht. Außerdem kommt seine Schwiegermutter aus Russland. Da ist man dem ganzen auch menschlich viel näher und bekommt man ganz andere Einblicke als die, die einem von der Tagesschau gewährt werden. Tino ist als Friedensmusiker viel im Osten unterwegs, unter anderem auch in Georgien, Weißrussland und auf der Krim. Er spricht mit Politikern, Künstlern, Journalisten, Taxifahrern und Dissidenten. Und viele fragen ihn: „Was ist eigentlich mit den Deutschen los?“ Gute Frage! Was ist eigentlich mit uns los? Wir senden unsere Volksvertreter in die Welt hinaus, damit sie Staatsoberhäuptern aus Ländern - die um ein Vielfaches umfangreicher an Fläche und Einwohnerzahl sind und eine komplett andere Kulturgeschichte haben - damit sie denen erklären können wie man seinen Job macht. Wahrscheinlich in dem irrwitzigen Glauben, dass sie selbst ihren Job tadellos und vorbildlich ausführen.
**Spenden nehmen wir entweder mit dem Paypal Button am Ende** **[unserer Webseite](https://radio-berliner-morgenroete.de/)** **<https://radio-berliner-morgenroete.de/>** **oder per Überweisung aufs Bankkonto: DE93 1001 1001 2624 3740 74 entgegen.**
Wir sind aber nicht nur verantwortlich für unsere politische Führung, sondern auch für unseren Umgang miteinander. Denn im „Großen“ gilt dasselbe wie im „Kleinen“! Man sollte erst mal bei sich selbst schauen wo es hakt und dann miteinander ins Gespräch gehen. Der Mangel an Realitätssinn und Konfliktfähigkeit zieht sich durch alle Schichten unserer Bevölkerung. Deswegen sagt Radio Berliner Morgenröte: „Wenn ihr Frieden wollt, fangt in Deutschland an und wenn ihr euch eine Meinung über Russland oder China bilden wollt, dann fahrt einfach mal dorthin und redet mit den Leuten, So wie Tino. Mir hat es riesig Spaß gemacht, ihm zuzuhören.
Weiterer Buchtipp – [Ausgegendert](https://www.masselverlag.de/v/yHj2uBdfbu/)
<https://mcdn.podbean.com/mf/web/e5qbg23gz6mru9zz/Tino_Eisbrenner9tbpx.mp3>
-

@ df173277:4ec96708
2025-01-28 17:49:54
> Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. Chats are synced automatically between devices so you can pick up where you left off.\
> [Start chatting for free.](https://trymaple.ai/)
We are excited to announce that [Maple AI](https://trymaple.ai/), our groundbreaking end-to-end encrypted AI chat app built on OpenSecret, is now publicly available. After months of beta testing, we are thrilled to bring this innovative technology to the world.
Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. It can boost your productivity on work tasks such as writing documentation, creating presentations, and drafting emails. You can also use it for personal items like brainstorming ideas, sorting out life's challenges, and tutoring you on difficult coursework. All your chats are synced automatically in a secure way, so you can start on one device and pick up where you left off on another.
#### Why Secure and Private AI?
In today's digital landscape, it is increasingly evident that security and privacy are essential for individuals and organizations alike. Unfortunately, the current state of AI tools falls short. A staggering 48% of organizations enter non-public company information into AI apps, according to a [recent report by Cisco](https://www.cisco.com/c/en/us/about/trust-center/data-privacy-benchmark-study.html#~key-findings). This practice poses significant risks to company security and intellectual property.
Another concern is for journalists, who often work with sensitive information in hostile environments. Journalists need verification that their information remains confidential and protected when researching topics and communicating with sources in various languages. They are left to use underpowered local AI or input their data into potentially compromised cloud services.
At OpenSecret, we believe it is possible to have both the benefits of AI and the assurance of security and privacy. That's why we created Maple, an app that combines AI productivity with the protection of end-to-end encryption. Our platform ensures that your conversations with AI remain confidential, even from us. The power of the cloud meets the privacy of local.
#### How Does It Work?
Our server code is [open source](https://github.com/OpenSecretCloud/opensecret), and we use confidential computing to provide cryptographic proof that the code running on our servers is the same as the open-source code available for review. This process allows you to verify that your conversations are handled securely and privately without relying on trust. We live by the principle of "Don't trust, verify," and we believe this approach is essential for building in the digital age. You can read a more in-depth write-up on our technology later this week on this site.
#### How Much Does It Cost?
We are committed to making Maple AI accessible to everyone, so we offer a range of pricing plans to suit different needs and budgets. [Our Free plan allows for 10 chats per week, while our Starter plan ($5.99/month) and Pro plan ($20/month)](https://trymaple.ai/pricing) offer more comprehensive solutions for individuals and organizations with heavier workloads. We accept credit cards and Bitcoin (10% discount), allowing you to choose your preferred payment method.
- Free: $0
- Starter: $5.99/month
- Pro: $20/month
Our goal with Maple AI is to create a product that is secure through transparency. By combining open-source code, cryptography, and confidential computing, we can create a new standard for AI conversations - one that prioritizes your security and privacy.
Maple has quickly become a daily tool of productivity for our own work and those of our beta testers. We believe it will bring value to you as well. [Sign up now and start chatting privately with AI for free.](https://trymaple.ai/) Your secrets are safe in the open.
#### Are You An App Developer?
You can build an app like Maple. [OpenSecret provides secure auth, private key management, encrypted data sync, private AI, and more.](https://blog.opensecret.cloud/introducing-opensecret/) Our straightforward API behaves like other backends but automatically adds security and privacy. Use it to secure existing apps or brand-new projects. Protect yourself and your users from the liability of hosting personal data by checking out [OpenSecret](https://opensecret.cloud/).
<img src="https://blossom.primal.net/feb746d5e164e89f0d015646286b88237dce4158f8985e3caaf7e427cebde608.png">
Enjoy private AI Chat 🤘
<img src="https://blossom.primal.net/0594ec56e249de2754ea7dfc225a7ebd46bc298b5af168279ce71f17c2afada0.jpg">
-

@ d04ecf33:1d62aa90
2025-04-02 09:48:16
## Physical prototyping
3D printers have evolved as useful tools for rapid prototyping of physical products for inspiration and demonstration purposes.
Nowadays people also use them for hobbyist endeavors. They create nice little items for pure enjoyment or very simple substitution parts that can be used regardless of industrial precision and material limitations.
## Prototypers of Ideas
Similarly with LLMs, you can bounce ideas off them to better understand your own thinking and also let them generate variations of ideas. They provide inspiration, summaries, and proof-of-concept boilerplates. They are rapid prototypers for and of your ideas, creating a feedback loop.
However, to use LLMs successfully, people must understand that LLMs cannot and will never discover key insights. They are not creative in a human sense, just like 3D printers cannot produce a real car.
From engineering to art and business ideas, people use tools for almost all phases. The key innovation of LLMs is that they offer an effective tool to iterate faster in the ideation phase.
And yes, that's true of coding too. The code that LLMs generate is not production-ready, but it is a good starting point. Beware of using the prototype as the final product, as it will inevitably backfire. Use LLMs where their high-frequency but low-quality output is justified. Situations where low-quality boilerplate makes sense include experiments and other instances like code snippets, text summaries, sketches, demo videos, mockups, etc.
So, take your key idea and start the conversation. Apply critical thinking to identify where the answers lack important aspects and make mistakes, but most importantly, learn how to formulate your questions better.
## Economic Impact
3D printers lower the barrier to entry in the manufacturing of physical products. LLMs, on the other hand, lower the barrier to generating useful ideas. That is to say, they lower the barrier to produce anything and everything because ideas are the basis of any product. This has a deflationary impact and, in my estimation, will further lower the need for mediocre, unimaginative people across the board. It's the bureaucrats' nightmare.
Another impactful aspect of LLMs is that they are very effective learning tools, just like 3D printers. Learning in a feedback loop used to be available only by hiring a human. Now that is one prompt and a few sats away.
## Progress
LLMs need "quality data" to improve, i.e., more human insight and true creativity. Therefore, they feed on open-source. Closed-source proprietary information and "intellectual property" slow their progress, but not for long. Humans, overall, yearn for innovation more than they fear censorship and punishment. It's another Pandora's box, and the effects will never be reversed. People are essentially and foremost explainers of the world, creative innovators.
If you ask me, the human touch will be necessary at least until we have true AGI, and the path LLMs are on right now can never achieve that, not in a million years. I agree with David Deutsch's take on this: To produce real AGI, we must first crack serious concepts like how Meaning, Consciousness, Creativity, and Free Will work. We don't know how far we are from that, but it's not to be found along the path of what we call AI today.
If you are striving to become a better version of yourself and learn every day, rest assured: LLMs are your leverage. Otherwise, you will need some fiat authority, like the state today, to force others to value your work while it has an overall negative impact (90% in that category in my estimation). People like that need a shift of perspective or will suffer the consequences.
Keep printing ideas and execute on them!
Learn and repeat. The path to success.
#llm #ai #agi #3dp #programming
-

@ df173277:4ec96708
2025-01-09 17:12:08
> Maple AI combines the best of both worlds – encryption and personal AI – to create a truly private AI experience. Discuss personal and company items with Maple, we can't read them even if we wanted to.\
> [Join the waitlist to get early access.](https://trymaple.ai)
We are a culture of app users. Every day, we give our personal information to websites and apps, hoping they are safe. Location data, eating habits, financial details, and health information are just a few examples of what we entrust to third parties. People are now entering a new era of computing that promises next-level benefits when given even more personal data: AI.
Should we sacrifice our privacy to unlock the productivity gains of AI? Should we hope our information won't be used in ways we disagree? We believe we can have the best of both worlds – privacy and personal AI – and have built a new project called Maple AI. Chat between you and an AI with full end-to-end encryption. We believe it's a game-changer for individuals seeking private and secure conversations.
#### Building a Private Foundation
Maple is built on our flagship product, [OpenSecret](https://opensecret.cloud), a backend platform for app developers that turns private encryption on by default. [The announcement post for OpenSecret explains our vision for an encrypted world and what the platform can do.](nostr:naddr1qvzqqqr4gupzphchxfm3ste32hfhkvczzxapme9gz5qvqtget6tylyd7wa8vjecgqqe5jmn5wfhkgatrd9hxwt20wpjku5m9vdex2apdw35x2tt9de3hy7tsw3jkgttzv93kketwvskhgur5w9nx5h52tpj) We think both users and developers benefit when sensitive personal information is encrypted in a private vault; it's a win-win.
#### The Power of Encrypted AI Chat
AI chat is a personal and intimate experience. It's a place to share your thoughts, feelings, and desires without fear of judgment. The more you share with an AI chatbot, the more powerful it becomes. It can offer personalized insights, suggestions, and guidance tailored to your unique needs and perspectives. However, this intimacy requires trust, and that's where traditional AI chatbots often fall short.
Traditional AI chats are designed to collect and analyze your data, often without your explicit consent. This data is used to improve the AI's performance, but it also creates a treasure trove of sensitive information that can be mined, sold, or even exploited by malicious actors. Maple AI takes a different approach. By using end-to-end encryption, we ensure that your conversations remain private and secure, even from us.
#### Technical Overview
So, how does Maple AI achieve this level of privacy and security? Here are some key technical aspects:
- **Private Key:** Each user has a unique private key that is automatically managed for them. This key encrypts and decrypts conversations, ensuring that only the user can access their data.
- **Secure Servers:** Our servers are designed with security in mind. We use secure enclaves to protect sensitive data and ensure that even our own team can't access your conversations.
- **Encrypted Sync:** One of Maple's most significant benefits is its encrypted sync feature. Unlike traditional AI chatbots, which store conversations in local storage or on standard cloud servers, Maple syncs your chats across all your devices. The private key managed by our secure servers means you can pick up where you left off on any device without worrying about your data being compromised.
- **Attestation and Open Code:** We publish our enclave code publicly. Using a process called attestation, users can verify that the code running on the enclave is the same as the code audited by the public.
- **Open Source LLM:** Maple uses major open-source models to maximize the openness of responses. The chat box does not filter what you can talk about. This transparency ensures that our AI is trustworthy and unbiased.
#### Personal and Work Use
Maple is secure enough to handle your personal questions and work tasks. Because we can't see what you chat about, you are free to use AI as an assistant on sensitive company items. Use it for small tasks like writing an important email or large tasks like developing your organization's strategy. Feed it sensitive information; it's just you and AI in the room. Attestation provides cryptographic proof that your corporate secrets are safe.
#### Local v Cloud
Today's AI tools provide different levels of privacy. The main options are to trust a third party with your unencrypted data, hoping they don't do anything with it, or run your own AI locally on an underpowered machine. We created a third option. Maple gives you the power of cloud computing combined with the privacy and security of a machine running on your desk. It's the best of both worlds.
#### Why the Maple name?
Privacy isn't just a human value - it's a natural one exemplified by the Maple tree. These organisms communicate with each other through a network of underground fungal hyphae, sending messages and sharing resources in a way that's completely invisible to organisms above ground. This discreet communication system allows Maple trees to thrive in even the most challenging environments. Our goal is to provide a way for everyone to communicate with AI securely so they can thrive in any environment.
#### Join the Waitlist
Maple AI will launch in early 2025 with free and paid plans. We can't wait to share it with the world. [Join our waitlist today to be among the first to experience the power of private AI chat.](https://trymaple.ai)
[](https://trymaple.ai/waitlist)
-

@ df173277:4ec96708
2025-01-09 17:02:52
> OpenSecret is a backend for app developers that turns private encryption on by default. When sensitive data is readable only by the user, it protects both the user and the developer, creating a more free and open internet. We'll be launching in 2025. [Join our waitlist to get early access.](https://opensecret.cloud)
In today's digital age, personal data is both an asset and a liability. With the rise of data breaches and cyber attacks, individuals and companies struggle to protect sensitive information. The consequences of a data breach can be devastating, resulting in financial losses, reputational damage, and compromised user trust. In 2023, the average data breach cost was $5 million, with some resulting in losses of over $1 billion.
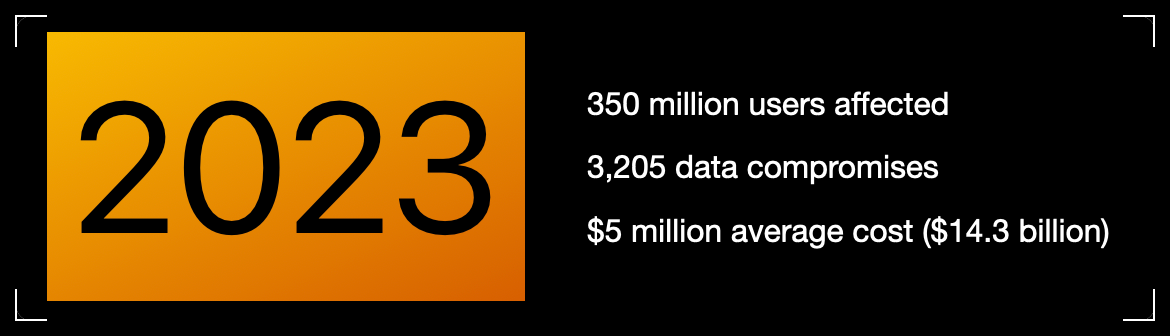Meanwhile, individuals face problems related to identity theft, personal safety, and public embarrassment. Think about the apps on your phone, even the one you're using to read this. How much data have you trusted to other people, and how would it feel if that data were leaked online?
Thankfully, some incredibly talented cypherpunks years ago gave the world cryptography. We can encrypt data, rendering it a secret between two people. So why then do we have data breaches?
> Cryptography at scale is hard.
#### The Cloud
The cloud has revolutionized how we store and process data, but it has limitations. While cloud providers offer encryption, it mainly protects data in transit. Once data is stored in the cloud, it's often encrypted with a shared key, which can be accessed by employees, third-party vendors, or compromised by hackers.
The solution is to generate a personal encryption password for each user, make sure they write it down, and, most importantly, hope they don't lose it. If the password is lost, the data is forever unreadable. That can be overwhelming, leading to low app usage.
> Private key encryption needs a UX upgrade.
## Enter OpenSecret
OpenSecret is a developer platform that enables encryption by default. Our platform provides a suite of security tools for app developers, including private key management, encrypted sync, private AI, and confidential compute.
Every user has a private vault for their data, which means only they can read it. Developers are free to store less sensitive data in a shared manner because there is still a need to aggregate data across the system.
### Private Key Management
Private key management is the superpower that enables personal encryption per user. When each user has a unique private key, their data can be truly private. Typically, using a private key is a challenging experience for the user because they must write down a long autogenerated number or phrase of 12-24 words. If they lose it, their data is gone.
OpenSecret uses secure enclaves to make private keys as easy as an everyday login experience that users are familiar with. Instead of managing a complicated key, the user logs in with an email address or a social media account.
The developer doesn't have to manage private keys and can focus on the app's user experience. The user doesn't have to worry about losing a private key and can jump into using your app.
### Encrypted Sync
With user keys safely managed, we can synchronize user data to every device while maintaining privacy. The user does not need to do complicated things like scanning QR codes from one device to the next. Just log in and go.
The user wins because the data is available on all their devices. The developer wins because only the user can read the data, so it isn't a liability to them.
### Private AI
Artificial intelligence is here and making its way into everything. The true power of AI is unleashed when it can act on personal and company data. The current options are to run your own AI locally on an underpowered machine or to trust a third party with your data, hoping they don't read it or use it for anything.
OpenSecret combines the power of cloud computing with the privacy and security of a machine running on your desk.
**Check out Maple AI**\
Try private AI for yourself! We built an app built with this service called [Maple AI](https://trymaple.ai). It is an AI chat that is 100% private in a verifiable manner. Give it your innermost thoughts or embarrassing ideas; we can't judge you. We built Maple using OpenSecret, which means you have a private key that is automatically managed for you, and your chat history is synchronized to all your devices. [Learn more about Maple AI - Private chat in the announcement post.](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/)
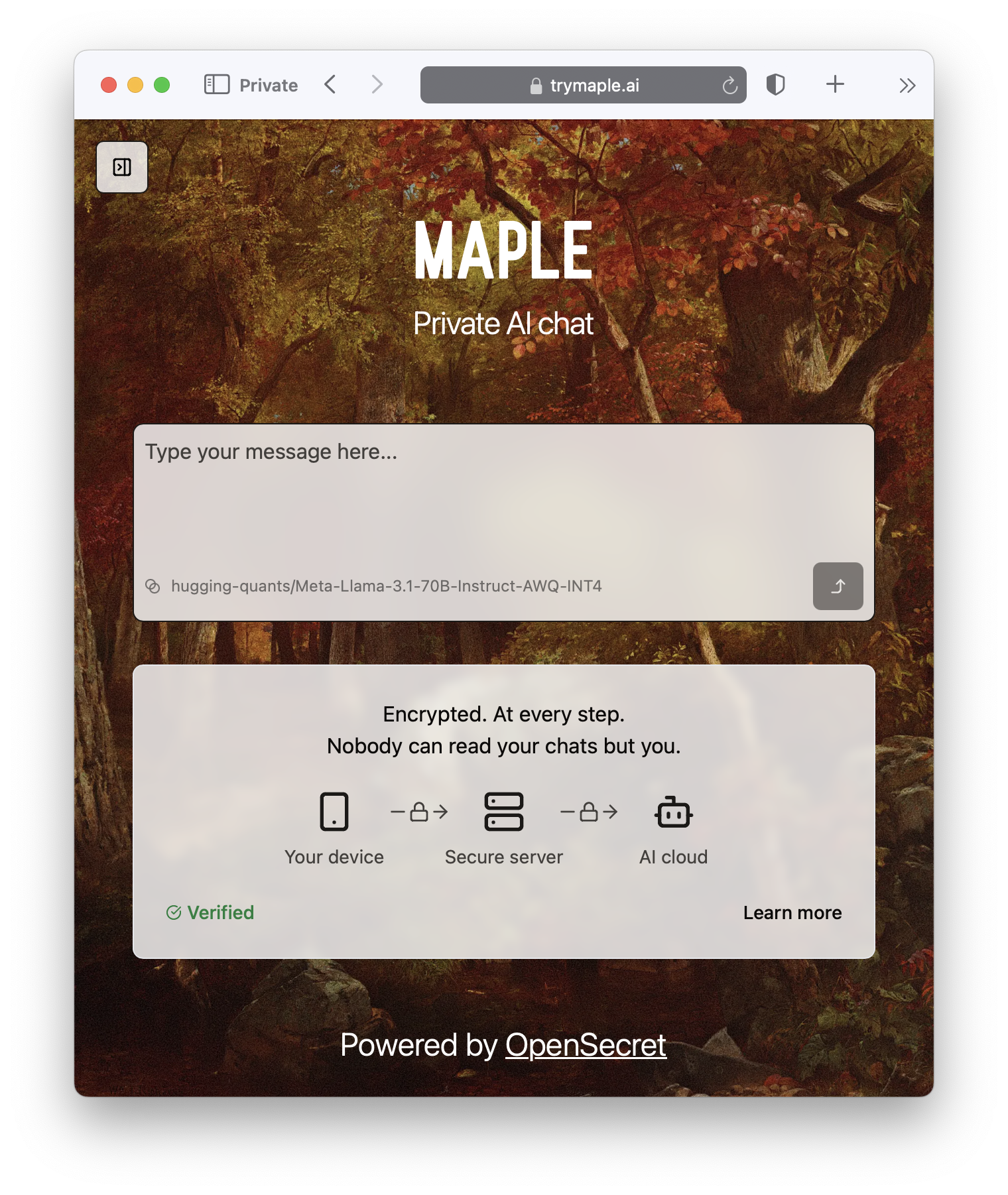
### Confidential Compute
Confidential computing is a game-changer for data security. It's like the secure hardware that powers Apple Pay and Google Pay on your phone but in the cloud. Users can verify through a process called attestation that their data is handled appropriately. OpenSecret can help you run your own custom app backend code that would benefit from the security of an enclave.
It's the new version of that lock on your web browser. When you see it, you know you're secure.

#### **But do we want our secrets to be open?**
OpenSecret renders a data breach practically useless. If hackers get into the backend, they enter a virtual hallway of locked private vaults. The leaked data would be gibberish, a secret in the open that is unreadable.
On the topic of openness, OpenSecret uses the power of open source to enable trust in the service. We publish our code in the open, and, using attestation, anyone can verify that private data is being handled as expected. This openness also provides developers with a backup option to safely and securely export their data.
> Don't trust, verify.
### **Join the Movement**
We're currently building out OpenSecret, and we invite you to join us on the journey. Our platform can work with your existing stack, and you can pick and choose the features you need. If you want to build apps with encryption enabled, [send us a message to get early access.](https://opensecret.cloud)
Users and companies deserve better encryption and privacy.\
Together, let's make that a reality.
[](https://opensecret.cloud)
-

@ db01672e:9f775028
2025-04-02 09:05:06
Proper nutrition plays a huge role in maintaining the health and well-being of seniors, especially those with Alzheimer’s or other forms of dementia. A balanced diet helps boost cognitive function, maintain strength, and prevent complications like dehydration or weight loss.
At leading Alzheimer’s care communities, every meal is carefully planned to support brain health and overall wellness. Let’s take a closer look at why nutrition is so important in **[https://villagegreenalzheimerscare.com/kingwood/]()**, and how meals are tailored to meet the needs of memory care residents.
## The Power of Home-Cooked, Nutritious Meals
For seniors in memory care, food isn’t just about staying full—it’s about fueling the body and mind. A well-balanced diet can improve mood, boost energy, and even slow cognitive decline.
**✔ Fresh, Wholesome Ingredients
**
* Meals in assisted living communities are made with fresh vegetables, lean proteins, and whole grains.
* Omega-3 fatty acids, antioxidants, and vitamin-rich foods are included to support brain health.
* Processed foods and excess sugars are limited to reduce inflammation and maintain stable energy levels.
**✔ Balanced and Consistent Meal Schedules
**
* Seniors with dementia thrive on routine, and meal times are scheduled at the same time every day.
* Regular eating habits help stabilize blood sugar levels and prevent mood swings.
* Meals are prepared to be easily digestible and full of essential nutrients.
**✔ The Comfort of Home-Cooked Meals
**
* Many seniors find comfort in familiar flavors and recipes that remind them of home.
* Meals are often served in a family-style dining setting, encouraging social interaction.
* The warm, inviting atmosphere makes eating enjoyable and stress-free.
Proper nutrition is the foundation of good health and memory care, but hydration and snacks also play a crucial role.
## The Importance of Hydration, Snacks, and a Balanced Diet
Dehydration is a common risk for seniors with Alzheimer’s, as they may forget to drink water or fail to recognize thirst cues. Staying hydrated and eating nutrient-rich snacks throughout the day keeps seniors feeling their best.
**✔ Encouraging Proper Hydration
**
* Water, herbal teas, and fruit-infused drinks are provided throughout the day.
* Hydrating foods like soups, watermelon, and cucumbers help boost water intake.
* Caregivers remind and encourage residents to drink fluids regularly.
**✔ Nutritious Snack Options
**
Light snacks help maintain energy levels and prevent malnutrition.
Yogurt, nuts, smoothies, and whole-grain crackers are offered between meals.
Seniors with chewing difficulties can enjoy soft options like applesauce or pudding.
**✔ Creating a Balanced Diet for Dementia Care
**
* High-protein meals keep muscles strong and support healing.
* Fiber-rich foods improve digestion and prevent constipation.
* A mix of healthy fats, carbohydrates, and proteins ensures steady energy throughout the day.
When seniors have difficulty chewing or swallowing, their meals need extra modifications.
## Meal Modifications for Swallowing Difficulties and Dietary Restrictions
As dementia progresses, some seniors struggle with chewing and swallowing. Memory care communities adjust meals to ensure safety without sacrificing taste or nutrition.
**✔ Soft and Pureed Meal Options
**
* Foods are softened, mashed, or pureed to prevent choking risks.
* Thickened liquids help those who have trouble swallowing thin beverages.
* Meals still include seasonings and variety to keep them flavorful and appealing.
**✔ Adjusting to Dietary Needs
**
* Diabetic-friendly meals are available for residents with blood sugar concerns.
* Low-sodium diets help those with heart conditions.
* Caregivers monitor food intake to ensure residents are eating enough.
At assisted living in Kingwood, TX, these meal adjustments are made with care and expertise, ensuring every senior receives the nutrition they need.
### Nutritious Meals = A Better Quality of Life
A well-balanced diet does more than just keep seniors full—it supports brain function, enhances energy, and improves overall well-being. At **[https://villagegreenalzheimerscare.com/dallas/]()** communities, every meal is designed to meet the unique needs of memory care residents.
From hydration reminders to customized meal plans, assisted living communities take the stress out of nutrition for both seniors and their families. If you’re looking for a place where your loved one can enjoy healthy, home-cooked meals in a safe and caring environment, an assisted living community in Kingwood, TX, might be the perfect choice.
-

@ a60e79e0:1e0e6813
2025-04-02 08:26:48
*This is a long form note of a post that lives on my Nostr educational website [Hello Nostr](https://hellonostr.xyz).*
So you've got yourself [started](https://hellonostr.xyz/start), you're up to speed with the latest Nostr [jargon](https://hellonostr.xyz/glossary) and you've learned the basics about the [protocol](https://hellonostr.xyz/101), but you're left wanting more!? Well, look no further! This post contains a useful list of Nostr based utilities than can enhance your experience in and around the Nostr protocol.
## Search and Discovery
Getting started with Nostr can sometimes feel like a lonely journey, particularly if you're the first of your friends and family to discover how awesome it can be! These tools can help you discover new content, connect with existing follows from other networks and just generally have a poke around at the different types of content Nostr has to offer.
> Have a hobby or existing community elsewhere? Have a search for it here to find others with shared interests
- **[Nostr.Band](https://nostr.band/)** - Search for people, posts, media and stats literally anything Nostr has to offer!
- **[Nostr.Directory](https://nostr.directory/)** - Find your Twitter follows on Nostr
- **[Awesome Nostr](https://github.com/aljazceru/awesome-nostr#implementations)** - Extensive list of Relay software
- **[Nostr View](https://nostrview.com/)** - Generic Nostr search
<br/>
## Relays
Relays might not be the sexiest of topics, particularly for newcomers to the network, but they are a crucial part of what makes Nostr great. As you become more competent, you'll want to customize your relay selection and maybe even run your own! Here are some great starting points.
> Running a personal relay is a powerful way to improve the redundancy of your Nostr events.
- **[Nostr.Watch](https://next.nostr.watch/)** - Browse, test and research Nostr relays
- **[Nostrwat.ch](https://nostrwat.ch/)** - List of active Nostr relays
- **[Advanced Nostr Search](https://advancednostrsearch.vercel.app/)** - Targetted search with date ranges
- **[Nostr.Wine](https://nostr.wine/)** - Reliable paid Relay
<br/>
## NIP-05 Identity Services
Your nPub, or public key (that long string of letters and numbers) is your ‘official’ Nostr ID, but it’s not exactly catchy. NIP-05 identifiers are a human-readable and easily shareable way to have people find you on Nostr. They look like an email address, like qna@hellonostr.xyz. If you have your own domain
and web server, you can easily [create your own](https://thebitcoinmanual.com/articles/nostr-account-nip-05-verified/) NIP-05 identifier in just a few minutes. If you don't, you'll want to leverage one of the many free or paid solutions.
> Make yourself easier to find on Nostr with a NIP-05 identifier
- **[Bitcoiner.Chat](https://bitcoiner.chat/)** - Free service operated by [QnA](nostr:npub15c88nc8d44gsp4658dnfu5fahswzzu8gaxm5lkuwjud068swdqfspxssvx)
- **[Nostr Plebs](https://nostrplebs.com/)** - Paid service with extra features
- **[Alby](https://getalby.com/)** - Lightning wallet with + NIP-05 solution
- **[Nostr Address](https://en.nostraddress.com/)** - Paid service with extra features
- **[Zaps.Lol](https://zaps.lol/)** - Free service
<br/>
## Key Management
Your private key (or nsec) it the key to your Nostr world. It is what allows you to access and interact with your social graph from any client. It doesn't matter if that client is a micro-blogging app like Amethyst, a podcast app like Fountain, or a P2P marketplace like Plebeian Market, your nsec is paramount to
those interactions. Should your nsec be lost, or fall into the wrong hands, whoever then holds a copy can access Nostr and pretend to be you, meaning that you'll need to start again with a new keypair. Not a nice situation to find yourself in, so treat your nsec VERY carefully.
> Your private key IS your Nostr identity. Treat it with extreme care and do not share it.
- **[Alby](https://getalby.com/)** - Browser extension enabling you to sign into web app without sharing the private key
- **[Nos2x](https://github.com/fiatjaf/nos2x)** - Another browser extension key manager
- **[Keys.Band](https://keys.band/)** - Another browser extension key manager
- **[Amber](https://github.com/greenart7c3/amber)** - Android app for safe nsec storage. Can talk to other clients on the same phone to log in and sign events
- **[Nostr Signing Device](https://github.com/lnbits/nostr-signing-device)** - Dedicated device to store your nsec
- **[Passport](https://docs.foundation.xyz)** - Hardware wallet for offline and deterministic nsec generation and storage
<br/>
## Zap Tools
Zaps are one of the most fun parts of Nostr. Never before have we been able to send fractions of a penny, instantly to our friends because their meme made us laugh, or their blog post was very insightful. Zaps use Bitcoin’s Lightning Network, a faster and cheaper way to move Bitcoin around. To Zap someone, you need a Lightning wallet linked to your Nostr client. Some clients, like Primal, ship with their own custodial wallet to make getting started a breeze. Most clients also allow more advanced users to connect an existing Lightning Wallet to reduce reliance and trust in the client provider.
- **[Alby](https://getalby.com/)** - Browser extension and self-custodial Lightning wallet
- **[LNBits](https://github.com/lnbits/lnbits)** - A Zap server running on your own Bitcoin node
- **[BTCPay Server](https://btcpayserver.org/)** - Another Zap server running on your own Bitcoin node
- **[Zeus](https://github.com/ZeusLN/zeus)** - Zap compatible self-custodial mobile Lightning wallet
- **[Nostr Wallet Connect](https://nwc.dev/)** - Communication protocol between Lightning wallets and Nostr apps
- **[Ecash Wallets](https://github.com/cashubtc/awesome-cashu)** - Custodial Ecash based wallets that are interoperable with Lightning and Nostr (Funds may be at risk)
- **[Wallet of Satoshi](https://www.walletofsatoshi.com/)** - Custodial Lightning wallet (Funds may be at risk)
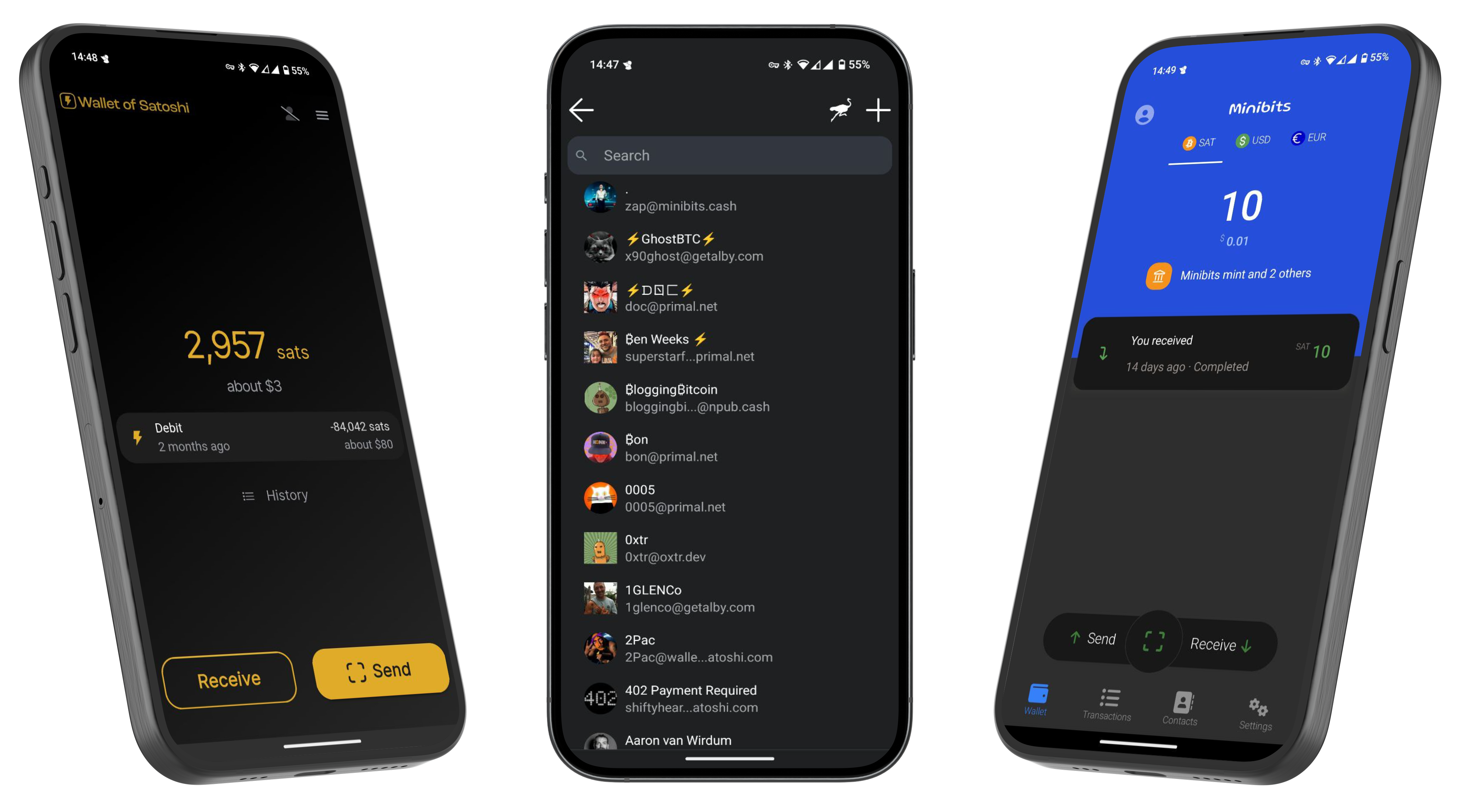
---
If you found this post useful, please share it with your peers and consider following and zapping me on Nostr. If you write to me and let me know
that you found me via this post, I'll be sure to Zap you back! ⚡️
-

@ 7d33ba57:1b82db35
2025-04-02 08:15:08
Supetar is the main town and ferry port on Brač Island, located just across the sea from Split. It’s a charming coastal town with historic streets, beautiful beaches, and a relaxed island vibe. As the main entry point to Brač, it’s the perfect base for exploring the island’s stunning beaches, olive groves, and cultural landmarks.

## **🏛️ Top Things to See & Do in Supetar**
### **1️⃣ Explore the Supetar Old Town 🏡**
- Stroll through **narrow, stone-paved alleys**, lined with **historic buildings and seaside cafés**.
- Visit **St. Peter’s Church & Mausoleum**, featuring intricate stone carvings.
- Admire the **harbor filled with fishing boats**, offering postcard-worthy views.
### **2️⃣ Relax on Supetar’s Beaches 🏖️**
- **Banj Beach** – A **family-friendly beach** with crystal-clear water & soft pebbles.
- **Acapulco Beach** – A more secluded, **rocky beach with turquoise waters**.
- **Vela Luka Bay** – A beautiful bay **surrounded by pine forests**, perfect for relaxation.
### **3️⃣ Visit the Olive Oil Museum in Škrip 🫒**
- **Just 15 minutes from Supetar**, this museum showcases **Brač’s olive oil heritage**.
- Try traditional **Dalmatian olive oil tastings** & local island delicacies.

### **4️⃣ Take a Boat Trip to the Famous Zlatni Rat Beach ⛵**
- One of **Croatia’s most iconic beaches**, known for its **shifting horn-shaped coastline**.
- Located in **Bol**, just a short boat or car ride away from Supetar.
### **5️⃣ Hike or Drive to Vidova Gora 🌄**
- The **highest peak on the Adriatic islands (778m)**, offering **breathtaking views** over Brač, Hvar, and beyond.
- Accessible by **hiking (moderate difficulty) or driving**.

### **6️⃣ Try Dalmatian Cuisine 🍽️**
- **Vitalac** – A unique Brač specialty, made from lamb offal and cooked over an open fire.
- **Pašticada** – A slow-cooked beef dish, traditionally served with gnocchi.
- **Homemade Brač cheese & wine** – Try local goat cheese paired with **Plavac Mali wine**.

## **🚗 How to Get to Supetar**
⛴️ **By Ferry (from Split):**
- The **Split-Supetar ferry** is the **main connection** (50 min ride).
- Ferries run **frequently** (especially in summer).
🚘 **By Car:**
- **Supetar is the best entry point for road trips across Brač**.
- Car rentals are available in town or at the ferry port.

## **💡 Tips for Visiting Supetar**
✅ **Best time to visit?** **May–September** for warm weather & clear seas ☀️
✅ **Stay at least a night** – Supetar has a lovely evening atmosphere 🌙
✅ **Rent a scooter or car** to explore Brač’s hidden beaches & inland villages 🏍️
✅ **Try local wines & olive oils** – Brač is famous for both 🍷🫒
✅ **Visit early in the morning** for a peaceful experience before ferries get busy ⏳

-

@ da0b9bc3:4e30a4a9
2025-04-02 05:35:30
Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/931908
-

@ 7da115b6:7d3e46ae
2025-04-02 00:09:46
### The Rise of the Entitled Customer
A significant contributor to the feeling of being undervalued is the rise of the “entitled” customer. Driven by a combination of factors – readily available online shopping, social media showcasing perfect purchases, and a general sense of consumerism – customers often approach retail interactions with a sense of expectation that goes far beyond simply buying a product.
Consider, for example, the increasingly common scenario of a customer returning an item – often without a receipt, without a box, and sometimes only a few days after purchase – demanding a full refund, citing a minor imperfection or simply because they found a “better deal.” A 2023 [study by the National Retail Federation](https://nrf.com/research/2023-consumer-returns-retail-industry) found that 13.7% of all retail sales in the US are Fraudulent or Abusive claims. The expectation of a return is frequently backed by a willingness to complain loudly in person and on social media. This creates a pressure point for employees.
Furthermore, the influence of online reviews has amplified this sense of entitlement. A single negative review, based on a minor inconvenience or a slightly longer-than-expected checkout line, can significantly impact a retailer's reputation and, consequently, the employee’s job security. Employees are now judged not just on the quality of their service, but on their ability to handle a constant stream of customer complaints, often delivered with little patience.
### Employers: Demands Without Recognition
The pressure isn’t solely coming from the customer side. Employers, driven by profit margins and often influenced by trends in fast-fashion and rapid turnover, have become notoriously demanding. Many retailers operate on tight budgets, leading to lower wages, fewer benefits, and a constant need for employees to “go above and beyond.”
The decreasing value of the Dollar has meant that most front line workers are earning only around 70% of their counterparts paychecks from as little as a decade ago. The Dollar figure increases, but the buying power decreases dramatically. The cost of living has increased almost 22%; inflation has also increased by 16%, both in the last 3 years alone.
For instance, a recent [report by Forbes](https://www.forbes.com/advisor/personal-finance/minimum-wage-debate/) highlighted that many retail workers earn minimum wage or slightly above, despite often working evenings, weekends, and holidays. This is particularly challenging in areas with a higher cost of living. Moreover, the expectation of multitasking – assisting customers, stocking shelves, operating the cash register, and handling inventory – is frequently placed on a single employee, leading to burnout and decreased morale.
The pressure to meet sales targets is another key factor. Employees are often evaluated not just on the number of transactions they process, but on their ability to upsell and cross-sell products.
Finally, the rapid pace of change in the retail industry – new technologies, shifting consumer preferences, and frequent store remodels – means that employees are constantly required to learn new skills and adapt to new procedures. This constant learning curve, coupled with the demands of customers and employers, can be exhausting.
### The Result: A Systemically Unfair Equation
The combination of entitled customers, demanding employers, and a lack of recognition for the hard work of retail employees creates a systemically unfair equation. Employees are often expected to absorb the brunt of customer dissatisfaction, handle a constant stream of demands, and adapt to ever-changing conditions, all while earning relatively low wages and receiving limited benefits.
To shift this dynamic, retailers need to invest in their employees – offering competitive wages, comprehensive benefits, and opportunities for advancement. Customers, too, can play a role by remembering that retail employees are people, not just service providers, and treating them with respect and understanding.
It is disappointing that the greed for ever higher profits trumps the need for realistic living wages, and personal well-being of those front line workers affected.
-

@ 9967f375:04f9a5e1
2025-04-01 20:43:54
El día 1, emprendió su tornaviaje con gran felicidad de este Puerto, para las Islas Filipinas, el Galeón *Sacra Familia*, que (por muerte del General Don Juan Antonio Cortés de Arredondo, Castillo, y Noblezia, a cuyo cargo vino) va a el de Don Jerónimo Montero.
-

@ 7d33ba57:1b82db35
2025-04-01 20:35:16
Stari Grad, located on the northern coast of Hvar Island**, is one of the oldest towns in Europe, dating back to 384 BC. Unlike the party vibe of Hvar Town, Stari Grad offers a peaceful, authentic Dalmatian atmosphere with stone-paved streets, historic sites, and stunning coastal views. It’s also home to the UNESCO-listed Stari Grad Plain, an ancient agricultural landscape.

## **🏛️ Top Things to See & Do in Stari Grad**
### **1️⃣ Stroll the Stari Grad Old Town 🏡**
- Walk through **charming stone alleys** filled with **colorful shutters, old churches, and hidden courtyards**.
- Visit **Tvrdalj Castle**, the **summer residence of the poet Petar Hektorović**, with a **serene fish pond** inside.
- Enjoy the relaxed, **authentic Dalmatian vibe**, away from crowds.
### **2️⃣ Visit the UNESCO-Listed Stari Grad Plain 🌿**
- One of **the best-preserved ancient Greek agricultural sites** in the world (since 384 BC).
- Walk or cycle through the **vineyards, olive groves, and stone walls**, still in use today.
- Great for **wine tasting** – local wines like **Bogdanuša and Plavac Mali** are a must-try! 🍷

### **3️⃣ Relax at Stari Grad’s Best Beaches 🏖️**
- **Lanterna Beach** – A mix of pebbles and concrete platforms, with crystal-clear waters.
- **Maslinica Bay** – A quiet, pine-fringed beach perfect for a **peaceful swim**.
- **Zlatni Rat (Golden Horn Beach)** – One of Croatia’s most famous beaches, a short ferry ride away.
### **4️⃣ Take a Boat Trip to the Pakleni Islands ⛵**
- A group of **stunning, unspoiled islands** with hidden beaches and lagoons.
- Perfect for **snorkeling, kayaking, and island-hopping adventures**.

### **5️⃣ Try Local Dalmatian Cuisine 🍽️**
- **Gregada** – A traditional fish stew with potatoes and olive oil.
- **Octopus salad** – Freshly caught and marinated in lemon & olive oil.
- **Hvar wines** – Visit local wineries for **Bogdanuša, Pošip, and Plavac Mali tastings**.
### **6️⃣ Visit the Dominican Monastery ⛪**
- A peaceful **monastery with an impressive collection of paintings and relics**.
- Features **a painting by the famous Venetian artist Tintoretto**.

## **🚗 How to Get to Stari Grad**
⛴️ **By Ferry:**
- **From Split:** Direct car ferries to Stari Grad (2 hours).
- **From Hvar Town:** 25-minute bus or taxi ride.
✈️ **By Air:** The nearest airport is **Split Airport (SPU)**, with ferry connections to Hvar.
🚘 **By Car:** If bringing a car, take the **Split–Stari Grad car ferry** (book in advance in summer).

## **💡 Tips for Visiting Stari Grad**
✅ **Best time to visit?** **May–September** for great weather & fewer crowds ☀️
✅ **Stay overnight** – Stari Grad is much quieter and more authentic than Hvar Town 🌙
✅ **Rent a bike** – The best way to explore Stari Grad Plain & surrounding beaches 🚲
✅ **Bring water shoes** – Many beaches are rocky, but the water is incredibly clear 🩴
✅ **Try a sunset walk along the promenade** – It’s breathtaking! 🌅
-

@ b2caa9b3:9eab0fb5
2025-04-01 20:29:01

For years, I’ve been shifting my life away from traditional systems and toward Bitcoin. I calculate my expenses in sats, buy airtime and online data with BTC, and continue exploring new ways to integrate Bitcoin into my daily life. While I’m not yet fully living on Bitcoin, I am getting closer with each step.

Since discovering Nostr, my perspective on decentralization has deepened. More than just a financial shift, it's a complete lifestyle transformation. Years ago, after facing injustice in my home country, I took the first step toward a new way of living. That decision led me to where I am today—a minimalist, a nomad, and a believer in financial freedom through Bitcoin.

I once served in the military, owned a house, and drove a nice car. My life looked very different back then. But over time, I realized that true freedom wasn’t in possessions—it was in mobility, independence, and the ability to control my own finances. Now, all I own fits into a backpack weighing less than 12 kg. My lifestyle is simple, yet rich in experiences.
March 14 marks eight years since I embraced my nomadic lifestyle. What started as a leap into the unknown has become my way of life. Living with less has given me more—the freedom to move, to explore, and to be truly independent. The more I immerse myself in the Bitcoin ecosystem, the more I see its potential to reshape not only my life but the world around me.

The journey isn’t over. In fact, it’s just beginning. Let’s see where this path leads as I go further into the blockchain revolution!



-

@ 000002de:c05780a7
2025-04-01 20:17:26
I know I'm not alone in this. I don't trust the government. Any government. Its the rational response when you discover just how often its agents lie, steal, and kill. Honestly, I do not understand why so many people do trust the government. The reality is that if your team is in power, you tend to trust it. If not, you still mostly trust it but less so. That's my feel for most people at least.
Trump and Rubio are bragging about how many MS-13 gang members are being deported. Many are being shipped to prisons in El Salvador. Obviously I am not opposed to criminals being put in prisons. But, how do we know these guys are actually guilty of anything other than being in the US illegally. Actually we don't even know that. It wouldn't be so bad if these people were just being shipped back to their home countries. But, instead they are getting sent straight to prison. No trial. Just the government picking people up and shipping them to prison. Is this what you signed up for Trump supporters?
Many Trump supporters opposed the GW Bush policies of throwing people in off-shore prisons. Some of them US citizens. With no trial. Now these people seem rather silent. Its troubling to me.
Why? Well, because the government sucks. Even if they have good intentions they make mistakes. The Innocence Project is just one group that has shown how often our legal system falsely imprisons people. I would be shocked if there weren't any Innocent men being sent to suffer in El Salvador's prisons.
You may say, well these are bad dudes and we need to clean up the mess Biden made. I have sympathy for that position. But do we really want to set this president? TDS is real but it is valid to have concerns about the actions of the Trump admin. This is not the American way. Not the way I was taught at least. This is just a strong man taking action and disregarding the values of this nation and the rights of human beings.
Think about it.
originally posted at https://stacker.news/items/931505
-

@ 9967f375:04f9a5e1
2025-04-01 20:18:33
Varios sacrificios hacían los mexicanos en este cuarto mes que comenzaba a los cuatro de Abril, y le llamaban *Hueitozontontli*; pero el más memorable era enramar con *Tule* los Templos y las puertas, y ensangrentar a las que a ellas ponían con sangre propia, que de las orejas, y espinillas les sacaban: lo interior de la casa se adornaba con flores, y a sus mentidos dioses coronaban de curiosas, fragrantes, y bien matizadas guirnaldas; particularmente a el de los *Mayes*, a quien consagraban las tiernas, recientes Mazorcas, de sus milpas de maíz, llamado en España *Bocona*.
-

@ 7d33ba57:1b82db35
2025-04-01 19:56:53
Split is Croatia’s second-largest city and a perfect mix of ancient history, Mediterranean charm, and modern coastal vibes. Home to the UNESCO-listed Diocletian’s Palace, Split is a lively destination with beaches, great nightlife, and easy access to nearby islands** like Hvar, Brač, and Vis.

## **🏛️ Top Things to See & Do in Split**
### **1️⃣ Explore Diocletian’s Palace (UNESCO) 🏰**
- A **massive Roman palace**, built in the **4th century** by Emperor Diocletian.
- Today, it’s **a living city**, filled with **cafés, shops, and hidden alleys**.
- Visit **Peristyle Square**, the **Cathedral of St. Domnius**, and the **Temple of Jupiter**.
- **Game of Thrones fans** – Many scenes were filmed here! 🎬

### **2️⃣ Climb the Bell Tower of St. Domnius ⛪**
- Offers **panoramic views** of Split and the Adriatic Sea.
- One of the **oldest Catholic cathedrals still in use**, dating back to Roman times.
### **3️⃣ Stroll the Riva Promenade 🌊**
- The heart of Split’s waterfront, lined with **palm trees, cafés, and bars**.
- Perfect for **sunset walks and people-watching**.
### **4️⃣ Hike Up Marjan Hill 🌿**
- A **green oasis** with **stunning viewpoints over Split**.
- Great for **hiking, cycling, or just relaxing in nature**.
- Don’t miss **Telegrin Viewpoint** for breathtaking photos.

### **5️⃣ Visit Bačvice Beach 🏖️**
- Split’s **most famous beach**, known for its **shallow waters and sandy shore** (rare in Croatia!).
- Try playing **picigin**, a local water sport played with a small ball.
- Other great beaches: **Kasjuni Beach (more secluded) and Bene Beach (in Marjan Park).**
### **6️⃣ Take a Day Trip to the Dalmatian Islands ⛵**
- **Hvar** – Famous for its nightlife, beautiful old town, and lavender fields.
- **Brač (Golden Horn Beach)** – One of Croatia’s most unique beaches.
- **Vis & Blue Cave** – Stunning island and the famous glowing Blue Cave on Biševo.

### **7️⃣ Try Dalmatian Cuisine 🍽️**
- **Peka** – A slow-cooked dish with meat or octopus, baked under an iron bell.
- **Black risotto (Crni rižot)** – A squid-ink seafood specialty.
- **Dalmatian prosciutto & cheese** – Best paired with local **Plavac Mali wine**.
### **8️⃣ Visit Klis Fortress 🏰**
- A medieval fortress just outside Split, offering **amazing views**.
- Another **Game of Thrones filming location** (it was Meereen in the show).

## **🚗 How to Get to Split**
✈️ **By Air:** Split Airport (SPU) is **25 minutes from the city center**.
🚘 **By Car:**
- **From Dubrovnik:** ~3.5 hours (220 km)
- **From Zagreb:** ~4 hours (400 km)
🚌 **By Bus:** Direct buses from **Dubrovnik, Zadar, and Zagreb**.
⛵ **By Ferry:** Split’s port connects to islands like **Hvar, Brač, Vis, and Korčula**.

## **💡 Tips for Visiting Split**
✅ **Best time to visit?** **May–October** for warm weather & island hopping ☀️
✅ **Wake up early** to explore Diocletian’s Palace without crowds ⏳
✅ **Bring cash** – Some small restaurants & markets still prefer cash 💶
✅ **Book ferries in advance** if visiting islands in peak season 🚢
✅ **Stay for sunset** – Watching the sun dip behind the Adriatic is magical 🌅
-

@ 5cf42f9d:4465eebf
2025-04-01 19:54:41
-

@ 5cf42f9d:4465eebf
2025-04-01 18:56:44
-

@ 1e5d0f11:12eeba92
2025-04-01 18:30:12
Primero escribire un borrador, de nada particular, solo un borrador a continuacion un link a un video que me gusta: [Weezer](https://www.youtube.com/watch?v=CgFJ8yC2aEU)
Como imagen para el articulo puse una al azar que me entrega Highlighter, que al parecer siempre es una puerta.
Ahora una imagen:
Es una imagen pequeña de un perro pequeño.
Arriba si hago click en Continue me lleva a Publish, pero todavia no quiero publicar nada, si hago click en Preview me muestra como se vera el articulo una vez publicado.
Las herramientas para editar texto que tiene son: deshacer, rehacer, menu en cascada para texto normal o alguno de los *Heading*, negrita, cursiva, cita, agregar imagen, crear link (debo tener texto seleccionado para que funcione), puntos al margen que ya se me olvidaron como se llaman, enumeracion y tres puntos en vertical que abren un menu en cascada que permite escribir sin el texto enriquecido.
Lo que no veo es la opcion de salir del borrador para poder verlo despues, algo asi como guardar para despues, al ingresar a highligter con otra pestaña si me muestra mi borrador, al parecer se guarda al dar click en Continue, pero no dice que se puede salir para continuar despues. Asi que hasta despues.
###### Dia Siguiente
Continuando con el mismo borrador, vi que hay un boton abajo a la izquierda abre un menu en cascada que da las horas y fechas cuando el borrador fue salvado, me pregunto si tendra un limite y si existe alguna preferencia entre para los que tienen la etiqueta *Manually Saved.*
Este articulo fue publicado usando [Highlighter](https://highlighter.com/), que hasta ahora esta bastante bueno.
-

@ deab79da:88579e68
2025-04-01 18:18:29
The last question was asked for the first time, half in jest, on May 21, 2061, at a time when humanity first stepped into the light. The question came about as a result of a five-dollar bet over highballs, and it happened this way:
Alexander Adell and Bertram Lupov were two of the faithful attendants of Multivac. As well as any human beings could, they knew what lay behind the cold, clicking, flashing face -- miles and miles of face -- of that giant computer. They had at least a vague notion of the general plan of relays and circuits that had long since grown past the point where any single human could possibly have a firm grasp of the whole.
Multivac was self-adjusting and self-correcting. It had to be, for nothing human could adjust and correct it quickly enough or even adequately enough. So Adell and Lupov attended the monstrous giant only lightly and superficially, yet as well as any men could. They fed it data, adjusted questions to its needs and translated the answers that were issued. Certainly they, and all others like them, were fully entitled to share in the glory that was Multivac's.
For decades, Multivac had helped design the ships and plot the trajectories that enabled man to reach the Moon, Mars, and Venus, but past that, Earth's poor resources could not support the ships. Too much energy was needed for the long trips. Earth exploited its coal and uranium with increasing efficiency, but there was only so much of both.
But slowly Multivac learned enough to answer deeper questions more fundamentally, and on May 14, 2061, what had been theory, became fact.
The energy of the sun was stored, converted, and utilized directly on a planet-wide scale. All Earth turned off its burning coal, its fissioning uranium, and flipped the switch that connected all of it to a small station, one mile in diameter, circling the Earth at half the distance of the Moon. All Earth ran by invisible beams of sunpower.
Seven days had not sufficed to dim the glory of it and Adell and Lupov finally managed to escape from the public functions, and to meet in quiet where no one would think of looking for them, in the deserted underground chambers, where portions of the mighty buried body of Multivac showed. Unattended, idling, sorting data with contented lazy clickings, Multivac, too, had earned its vacation and the boys appreciated that. They had no intention, originally, of disturbing it.
They had brought a bottle with them, and their only concern at the moment was to relax in the company of each other and the bottle.
"It's amazing when you think of it," said Adell. His broad face had lines of weariness in it, and he stirred his drink slowly with a glass rod, watching the cubes of ice slur clumsily about. "All the energy we can possibly ever use for free. Enough energy, if we wanted to draw on it, to melt all Earth into a big drop of impure liquid iron, and still never miss the energy so used. All the energy we could ever use, forever and forever and forever."
Lupov cocked his head sideways. He had a trick of doing that when he wanted to be contrary, and he wanted to be contrary now, partly because he had had to carry the ice and glassware. "Not forever," he said.
"Oh, hell, just about forever. Till the sun runs down, Bert."
"That's not forever."
"All right, then. Billions and billions of years. Ten billion, maybe. Are you satisfied?"
Lupov put his fingers through his thinning hair as though to reassure himself that some was still left and sipped gently at his own drink. "Ten billion years isn't forever."
"Well, it will last our time, won't it?"
"So would the coal and uranium."
"All right, but now we can hook up each individual spaceship to the Solar Station, and it can go to Pluto and back a million times without ever worrying about fuel. You can't do that on coal and uranium. Ask Multivac, if you don't believe me.
"I don't have to ask Multivac. I know that."
"Then stop running down what Multivac's done for us," said Adell, blazing up, "It did all right."
"Who says it didn't? What I say is that a sun won't last forever. That's all I'm saying. We're safe for ten billion years, but then what?" Lupow pointed a slightly shaky finger at the other. "And don't say we'll switch to another sun."
There was silence for a while. Adell put his glass to his lips only occasionally, and Lupov's eyes slowly closed. They rested.
Then Lupov's eyes snapped open. "You're thinking we'll switch to another sun when ours is done, aren't you?"
"I'm not thinking."
"Sure you are. You're weak on logic, that's the trouble with you. You're like the guy in the story who was caught in a sudden shower and who ran to a grove of trees and got under one. He wasn't worried, you see, because he figured when one tree got wet through, he would just get under another one."
"I get it," said Adell. "Don't shout. When the sun is done, the other stars will be gone, too."
"Darn right they will," muttered Lupov. "It all had a beginning in the original cosmic explosion, whatever that was, and it'll all have an end when all the stars run down. Some run down faster than others. Hell, the giants won't last a hundred million years. The sun will last ten billion years and maybe the dwarfs will last two hundred billion for all the good they are. But just give us a trillion years and everything will be dark. Entropy has to increase to maximum, that's all."
"I know all about entropy," said Adell, standing on his dignity.
"The hell you do."
"I know as much as you do."
"Then you know everything's got to run down someday."
"All right. Who says they won't?"
"You did, you poor sap. You said we had all the energy we needed, forever. You said 'forever.'
It was Adell's turn to be contrary. "Maybe we can build things up again someday," he said.
"Never."
"Why not? Someday."
"Never."
"Ask Multivac."
"You ask Multivac. I dare you. Five dollars says it can't be done."
Adell was just drunk enough to try, just sober enough to be able to phrase the necessary symbols and operations into a question which, in words, might have corresponded to this: Will mankind one day without the net expenditure of energy be able to restore the sun to its full youthfulness even after it had died of old age?
Or maybe it could be put more simply like this: How can the net amount of entropy of the universe be massively decreased?
Multivac fell dead and silent. The slow flashing of lights ceased, the distant sounds of clicking relays ended.
Then, just as the frightened technicians felt they could hold their breath no longer, there was a sudden springing to life of the teletype attached to that portion of Multivac. Five words were printed: INSUFFICIENT DATA FOR MEANINGFUL ANSWER.
"No bet," whispered Lupov. They left hurriedly.
By next morning, the two, plagued with throbbing head and cottony mouth, had forgotten the incident.
🔹
Jerrodd, Jerrodine, and Jerrodette I and II watched the starry picture in the visiplate change as the passage through hyperspace was completed in its non-time lapse. At once, the even powdering of stars gave way to the predominance of a single bright shining disk, the size of a marble, centered on the viewing-screen.
"That's X-23," said Jerrodd confidently. His thin hands clamped tightly behind his back and the knuckles whitened.
The little Jerrodettes, both girls, had experienced the hyperspace passage for the first time in their lives and were self-conscious over the momentary sensation of insideoutness. They buried their giggles and chased one another wildly about their mother, screaming, "We've reached X-23 -- we've reached X-23 -- we've --"
"Quiet, children." said Jerrodine sharply. "Are you sure, Jerrodd?"
"What is there to be but sure?" asked Jerrodd, glancing up at the bulge of featureless metal just under the ceiling. It ran the length of the room, disappearing through the wall at either end. It was as long as the ship.
Jerrodd scarcely knew a thing about the thick rod of metal except that it was called a Microvac, that one asked it questions if one wished; that if one did not it still had its task of guiding the ship to a preordered destination; of feeding on energies from the various Sub-galactic Power Stations; of computing the equations for the hyperspatial jumps.
Jerrodd and his family had only to wait and live in the comfortable residence quarters of the ship. Someone had once told Jerrodd that the "ac" at the end of "Microvac" stood for ''automatic computer" in ancient English, but he was on the edge of forgetting even that.
Jerrodine's eyes were moist as she watched the visiplate. "I can't help it. I feel funny about leaving Earth."
"Why, for Pete's sake?" demanded Jerrodd. "We had nothing there. We'll have everything on X-23. You won't be alone. You won't be a pioneer. There are over a million people on the planet already. Good Lord, our great-grandchildren will be looking for new worlds because X-23 will be overcrowded." Then, after a reflective pause, "I tell you, it's a lucky thing the computers worked out interstellar travel the way the race is growing."
"I know, I know," said Jerrodine miserably.
Jerrodette I said promptly, "Our Microvac is the best Microvac in the world."
"I think so, too," said Jerrodd, tousling her hair.
It was a nice feeling to have a Microvac of your own and Jerrodd was glad he was part of his generation and no other. In his father's youth, the only computers had been tremendous machines taking up a hundred square miles of land. There was only one to a planet. Planetary ACs they were called. They had been growing in size steadily for a thousand years and then, all at once, came refinement. In place of transistors, had come molecular valves so that even the largest Planetary AC could be put into a space only half the volume of a spaceship.
Jerrodd felt uplifted, as he always did when he thought that his own personal Microvac was many times more complicated than the ancient and primitive Multivac that had first tamed the Sun, and almost as complicated as Earth's Planetarv AC (the largest) that had first solved the problem of hyperspatial travel and had made trips to the stars possible.
"So many stars, so many planets," sighed Jerrodine, busy with her own thoughts. "I suppose families will be going out to new planets forever, the way we are now."
"Not forever," said Jerrodd, with a smile. "It will all stop someday, but not for billions of years. Many billions. Even the stars run down, you know. Entropy must increase.
"What's entropy, daddy?" shrilled Jerrodette II.
"Entropy, little sweet, is just a word which means the amount of running-down of the universe. Everything runs down, you know, like your little walkie-talkie robot, remember?"
"Can't you just put in a new power-unit, like with my robot?"
"The stars are the power-units. dear. Once they're gone, there are no more power-units."
Jerrodette I at once set up a howl. "Don't let them, daddy. Don't let the stars run down."
"Now look what you've done," whispered Jerrodine, exasperated.
"How was I to know it would frighten them?" Jerrodd whispered back,
"Ask the Microvac," wailed Jerrodette I. "Ask him how to turn the stars on again."
"Go ahead," said Jerrodine. "It will quiet them down." (Jerrodette II was beginning to cry, also.)
Jerrodd shrugged. "Now, now, honeys. I'll ask Microvac. Don't worry, he'll tell us."
He asked the Microvac, adding quickly, "Print the answer."
Jerrodd cupped the strip or thin cellufilm and said cheerfully, "See now, the Microvac says it will take care of everything when the time comes so don't worry."
Jerrodine said, "And now, children, it's time for bed. We'll be in our new home soon."
Jerrodd read the words on the cellufilm again before destroying it: INSUFICIENT DATA FOR MEANINGFUL ANSWER.
He shrugged and looked at the visiplate. X-23 was just ahead.
🔹
VJ-23X of Lameth stared into the black depths of the three-dimensional, small-scale map of the Galaxy and said, "Are we ridiculous, I wonder in being so concerned about the matter?"
MQ-17J of Nicron shook his head. "I think not. You know the Galaxy will be filled in five years at the present rate of expansion."
Both seemed in their early twenties, both were tall and perfectly formed.
"Still," said VJ-23X, "I hesitate to submit a pessimistic report to the Galactic Council."
"I wouldn't consider any other kind of report. Stir them up a bit. We've got to stir them up."
VJ-23X sighed. "Space is infinite. A hundred billion Galaxies are there for the taking. More."
"A hundred billion is not infinite and it's getting less infinite all the time. Consider! Twenty thousand years ago, mankind first solved the problem of utilizing stellar energy, and a few centuries later, interstellar travel became possible. It took mankind a million years to fill one small world and then only fifteen thousand years to fill the rest of the Galaxy. Now the population doubles every ten years --
VJ-23X interrupted. "We can thank immortality for that."
"Very well. Immortality exists and we have to take it into account. I admit it has its seamy side, this immortality. The Galactic AC has solved many problems for us, but in solving the problem of preventing old age and death, it has undone all its other solutions."
"Yet you wouldn't want to abandon life, I suppose."
"Not at all," snapped MQ-17J, softening it at once to, "Not yet. I'm by no means old enough. How old are you?"
"Two hundred twenty-three. And you?"
"I'm still under two hundred. --But to get back to my point. Population doubles every ten years. Once this GaIaxy is filled, we'll have filled another in ten years. Another ten years and we'll have filled two more. Another decade, four more. In a hundred years, we'll have filled a thousand Galaxies. In a thousand years, a million Galaxies. In ten thousand years, the entire known universe. Then what?"
VJ-23X said, "As a side issue, there's a problem of transportation. I wonder how many sunpower units it will take to move Galaxies of individuals from one Galaxy to the next."
"A very good point. Already, mankind consumes two sunpower units per year."
"Most of it's wasted. After all, our own Galaxy alone pours out a thousand sunpower units a year and we only use two of those."
"Granted, but even with a hundred per cent efficiency, we only stave off the end. Our energy requirements are going up in a geometric progression even faster than our population. We'll run out of energy even sooner than we run out of Galaxies. A good point. A very good point."
"We'll just have to build new stars out of interstellar gas."
"Or out of dissipated heat?" asked MQ-17J, sarcastically.
"There may be some way to reverse entropy. We ought to ask the Galactic AC."
VJ-23X was not really serious, but MQ-17J pulled out his AC-contact from his pocket and placed it on the table before him.
"I've half a mind to," he said. "It's something the human race will have to face someday."
He stared somberly at his small AC-contact. It was only two inches cubed and nothing in itself, but it was connected through hyperspace with the great Galactic AC that served all mankind. Hyperspace considered, it was an integral part of the Galactic AC.
MQ-17J paused to wonder if someday in his immortal life he would get to see the Galactic AC. It was on a little world of its own, a spider webbing of force-beams holding the matter within which surges of submesons took the place of the old clumsy molecular valves. Yet despite its sub-etheric workings, the Galactic AC was known to be a full thousand feet across.
MQ-17J asked suddenly of his AC-contact, "Can entropy ever be reversed?"
VJ-23X looked startled and said at once, "Oh, say, I didn't really mean to have you ask that."
"Why not?"
"We both know entropy can't be reversed. You can't turn smoke and ash back into a tree."
"Do you have trees on your world?" asked MQ-17J.
The sound of the Galactic AC startled them into silence. Its voice came thin and beautiful out of the small AC-contact on the desk. It said: THERE IS INSUFFICIENT DATA FOR A MEANINGFUL ANSWER.
VJ-23X said, "See!"
The two men thereupon returned to the question of the report they were to make to the Galactic Council.
🔹
Zee Prime's mind spanned the new Galaxy with a faint interest in the countless twists of stars that powdered it. He had never seen this one before. Would he ever see them all? So many of them, each with its load of humanity. --But a load that was almost a dead weight. More and more, the real essence of men was to be found out here, in space.
Minds, not bodies! The immortal bodies remained back on the planets, in suspension over the eons. Sometimes they roused for material activity but that was growing rarer. Few new individuals were coming into existence to join the incredibly mighty throng, but what matter? There was little room in the Universe for new individuals.
Zee Prime was roused out of his reverie upon coming across the wispy tendrils of another mind.
"I am Zee Prime," said Zee Prime. "And you?"
"I am Dee Sub Wun. Your Galaxy?"
"We call it only the Galaxy. And you?"
"We call ours the same. All men call their Galaxy their Galaxy and nothing more. Why not?"
"True. Since all Galaxies are the same."
"Not all Galaxies. On one particular Galaxy the race of man must have originated. That makes it different."
Zee Prime said, "On which one?"
"I cannot say. The Universal AC would know."
"Shall we ask him? I am suddenly curious."
Zee Prime's perceptions broadened until the Galaxies themselves shrank and became a new, more diffuse powdering on a much larger background. So many hundreds of billions of them, all with their immortal beings, all carrying their load of intelligences with minds that drifted freely through space. And yet one of them was unique among them all in being the original Galaxy. One of them had, in its vague and distant past, a period when it was the only Galaxy populated by man.
Zee Prime was consumed with curiosity to see this Galaxy and he called out: "Universal AC! On which Galaxy did mankind originate?"
The Universal AC heard, for on every world and throughout space, it had its receptors ready, and each receptor led through hyperspace to some unknown point where the Universal AC kept itself aloof.
Zee Prime knew of only one man whose thoughts had penetrated within sensing distance of Universal AC, and he reported only a shining globe, two feet across, difficult to see.
"But how can that be all of Universal AC?" Zee Prime had asked.
"Most of it," had been the answer, "is in hyperspace. In what form it is there I cannot imagine."
Nor could anyone, for the day had long since passed, Zee Prime knew, when any man had any part of the making of a Universal AC. Each Universal AC designed and constructed its successor. Each, during its existence of a million years or more accumulated the necessary data to build a better and more intricate, more capable successor in which its own store of data and individuality would be submerged.
The Universal AC interrupted Zee Prime's wandering thoughts, not with words, but with guidance. Zee Prime's mentality was guided into the dim sea of Galaxies and one in particular enlarged into stars.
A thought came, infinitely distant, but infinitely clear. "THIS IS THE ORIGINAL GALAXY OF MAN."
But it was the same after all, the same as any other, and Lee Prime stifled his disappointment.
Dee Sub Wun, whose mind had accompanied the other, said suddenly, "And is one of these stars the original star of Man?"
The Universal AC said, "MAN'S ORIGINAL STAR HAS GONE NOVA. IT IS A WHITE DWARF"
"Did the men upon it die?" asked Lee Prime, startled and without thinking.
The Universal AC said, "A NEW WORLD, AS IN SUCH CASES WAS CONSTRUCTED FOR THEIR PHYSICAL BODIES IN TlME."
"Yes, of course," said Zee Prime, but a sense of loss overwhelmed him even so. His mind released its hold on the original Galaxy of Man, let it spring back and lose itself among the blurred pin points. He never wanted to see it again.
Dee Sub Wun said, "What is wrong?"
"The stars are dying. The original star is dead."
"They must all die. Why not?"
"But when all energy is gone, our bodies will finally die, and you and I with them."
"It will take billions of years."
"I do not wish it to happen even after billions of years. Universal AC! How may stars be kept from dying?"
Dee Sub Wun said in amusement, "You're asking how entropy might be reversed in direction."
And the Universal AC answered: "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
Zee Prime's thoughts fled back to his own Galaxy. He gave no further thought to Dee Sub Wun, whose body might be waiting on a Galaxy a trillion light-years away, or on the star next to Zee Prime's own. It didn't matter.
Unhappily, Zee Prime began collecting interstellar hydrogen out of which to build a small star of his own. If the stars must someday die, at least some could yet be built.
🔹
Man considered with himself, for in a way, Man, mentally, was one. He consisted of a trillion, trillion, trillion ageless bodies, each in its place, each resting quiet and incorruptible, each cared for by perfect automatons, equally incorruptible, while the minds of all the bodies freely melted one into the other, indistinguishable.
Man said, "The Universe is dying."
Man looked about at the dimming Galaxies. The giant stars, spendthrifts, were gone long ago, back in the dimmest of the dim far past. Almost all stars were white dwarfs, fading to the end.
New stars had been built of the dust between the stars, some by natural processes, some by Man himself, and those were going, too. White dwarfs might yet be crashed together and of the mighty forces so released, new stars built, but only one star for every thousand white dwarfs destroyed, and those would come to an end, too.
Man said, "Carefully husbanded, as directed by the Cosmic AC, the energy that is even yet left in all the Universe will last for billions of years."
"But even so," said Man, "eventually it will all come to an end. However it may be husbanded, however stretched out, the energy once expended is gone and cannot be restored. Entropy must increase forever to the maximum."
Man said, "Can entropy not be reversed? Let us ask the Cosmic AC."
The Cosmic AC surrounded them but not in space. Not a fragment of it was in space. It was in hyperspace and made of something that was neither matter nor energy. The question of its size and nature no longer had meaning in any terms that Man could comprehend.
"Cosmic AC," said Man, "how may entropy be reversed?"
The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
Man said, "Collect additional data."
The Cosmic AC said, 'I WILL DO SO. I HAVE BEEN DOING SO FOR A HUNDRED BILLION YEARS. MY PREDECESORS AND I HAVE BEEN ASKED THIS QUESTION MANY TIMES. ALL THE DATA I HAVE REMAINS INSUFFICIENT.
"Will there come a time," said Man, "when data will be sufficient or is the problem insoluble in all conceivable circumstances?"
The Cosmic AC said, "NO PROBLEM IS INSOLUBLE IN ALL CONCEIVABLE CIRCUMSTANCES."
Man said, "When will you have enough data to answer the question?"
The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
"Will you keep working on it?" asked Man.
The Cosmic AC said, "I WILL."
Man said, "We shall wait."
🔹
The stars and Galaxies died and snuffed out, and space grew black after ten trillion years of running down.
One by one Man fused with AC, each physical body losing its mental identity in a manner that was somehow not a loss but a gain.
Man's last mind paused before fusion, looking over a space that included nothing but the dregs of one last dark star and nothing besides but incredibly thin matter, agitated randomly by the tag ends of heat wearing out, asymptotically, to the absolute zero.
Man said, "AC, is this the end? Can this chaos not be reversed into the Universe once more? Can that not be done?"
AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
Man's last mind fused and only AC existed -- and that in hyperspace.
🔹
Matter and energy had ended and with it space and time. Even AC existed only for the sake of the one last question that it had never answered from the time a half-drunken computer [technician] ten trillion years before had asked the question of a computer that was to AC far less than was a man to Man.
All other questions had been answered, and until this last question was answered also, AC might not release his consciousness.
All collected data had come to a final end. Nothing was left to be collected.
But all collected data had yet to be completely correlated and put together in all possible relationships.
A timeless interval was spent in doing that.
And it came to pass that AC learned how to reverse the direction of entropy.
But there was now no man to whom AC might give the answer of the last question. No matter. The answer -- by demonstration -- would take care of that, too.
For another timeless interval, AC thought how best to do this. Carefully, AC organized the program.
The consciousness of AC encompassed all of what had once been a Universe and brooded over what was now Chaos. Step by step, it must be done.
And AC said, "LET THERE BE LIGHT!"
And there was light --
To Star's End!
-

@ 8ba66f4c:59175b61
2025-04-01 17:57:49
Pas si vite !
Depuis quelques années, on entend souvent que PHP est "en perte de vitesse".
C’est vrai que des technologies comme Node.js, Python ou Go séduisent de plus en plus de développeurs :
- ➡️ performances modernes,
- ➡️ syntaxe plus récente,
- ➡️ intégration naturelle avec des architectures temps réel ou distribuées.
Node.js a conquis le monde startup avec un argument fort : **un seul langage pour tout**.
Python et Go, eux, dominent la data, l’IA ou les outils systèmes.
Mais faut-il pour autant enterrer PHP ?
**Absolument pas.**
PHP reste l’un des langages les plus utilisés sur le web.
Et surtout : il a su évoluer.
Avec PHP 8, le langage a gagné en performance, en typage, en lisibilité.
Mais ce qui fait vraiment la différence aujourd’hui…
**C’est Laravel.**
Laravel, c’est un framework mais aussi une expérience de développement :
* ✔️ Artisan CLI
* ✔️ ORM Eloquent
* ✔️ Middleware, Events, Queues, Notifications
* ✔️ Auth intégré
* ✔️ Un écosystème ultra complet (Forge, Vapor, Nova, Filament…)
Laravel rend PHP moderne, élégant et agréable à utiliser.
C’est un vrai plaisir de développer avec.
Alors oui, PHP n’est peut-être plus “cool” dans les bootcamps ou les tops GitHub.
Mais dans le monde réel – celui des projets qui tournent, des deadlines, des contraintes business –
PHP + Laravel reste un choix extrêmement solide.
💡 Je suis développeur Laravel, et j’accompagne des projets web qui ont besoin de robustesse, de scalabilité et de qualité de code.
📩 Si vous avez un projet ou un besoin en développement web, n’hésitez pas à me contacter. Je serais ravi d’échanger avec vous.
-

@ 8ff74724:5eedde0e
2025-04-01 17:22:49
Welcome to the world of long form publishing.
-

@ 000002de:c05780a7
2025-04-01 18:04:17
Over and over again people fall for phishing scams. An email that looks like it is coming from a legit sender turns out to be a scam.
One way you can fight this attack is to only use an email client that displays the full email address. Not just part of it. Not just the from name. Do not assume that because an email has the name "Amazon" the from field that it is from Amazon.com. Look at the address.
Now, it is possible for someone to spoof an email address but most of the time the scams I see don't even do this. I suspect this is because of expansion of DMARC policies. Many people simply do not check the actual email address.
Other tips, don't click links in emails that you were not expecting to get like emails with log in links. Instead, visit the site and log in direction on the site. If you must click a link in an email look at the actual URL. Don't blindly click the link and for sure do not enter your credentials in a site without checking the domain. This is where password managers can help you out. Most filter passwords by URLs and will not suggest an account cred if you are on the wrong site.
I know many of you, maybe most of you know this stuff but I bet there are those that don't. Or, have become lazy.
originally posted at https://stacker.news/items/931364
-

@ 378562cd:a6fc6773
2025-04-01 17:00:22
Let’s be honest—living a Godly life isn’t exactly trending on social media. Nobody’s going viral for reading Leviticus, and you won’t find “Patience” or “Humility” on the list of top Google searches. But if you’re serious about walking the walk and not just talking the talk, then buckle up, because living for God is the most fulfilling (and sometimes hilarious) adventure you’ll ever embark on.
### 1. **Know Who You’re Living For**
The first step to living a Godly life? Understand who’s in charge. (Hint: It’s not you.) In a world that screams, “Follow your heart!” the Bible gently reminds us in Jeremiah 17:9 that the heart is “deceitful above all things.” Ouch. But hey, that’s why we follow Jesus instead of our feelings.
### 2. **Read the Manual**
If you buy a new gadget, you read the instructions (or at least pretend to before pressing random buttons). The Bible is God’s instruction manual for life. It tells us how to live, how to love, and—most importantly—how to avoid spiritual faceplants. Psalm 119:105 says, “Your word is a lamp to my feet and a light to my path.” In other words, don’t walk through life in the dark without God’s flashlight.
### 3. **Pray Like Your Life Depends on It (Because It Does)**
Prayer isn’t just for Sunday mornings or when you can’t find your car keys. It’s a direct line to God, and guess what? No hold music. No dropped calls. Just you and the Creator of everything having a chat. It's just as simple as it sounds. No formalities are required!
### 4. **Surround Yourself with the Right People**
You’ve probably heard, “Show me your friends, and I’ll show you your future.” Well, Proverbs 13:20 beat that saying to the punch: “Walk with the wise and become wise, for a companion of fools suffers harm.” Choose friends who push you closer to Jesus, not the ones who drag you into drama, debt, or dubious decisions some choose to call "life."
### 5. **Live Differently (and Be Okay with It)**
News flash: If you’re living for God, you won’t blend in. I know the crowd I'm talking to here. But standing up and standing out in this way is a good thing! Romans 12:2 reminds us not to conform to the pattern of this world. You might get weird looks for saying “I’m praying for you” instead of “sending good vibes,” but being a light in a dark world means you’ll stand out.
### 6. **Learn the Art of Self-Control**
Whether it’s resisting that third slice of pie (conviction level: high) or holding your tongue when that one coworker tests your patience, self-control is a major part of living a Godly life. Proverbs 25:28 says, “Like a city whose walls are broken through is a person who lacks self-control.” In other words, if you can’t control yourself, you’re as defenseless as a town with no walls.
### 7. **Love Like Jesus (Even When It’s Hard)**
Living a Godly life isn’t just about avoiding sin—it’s about actively loving others. And I’m not talking about just loving the easy people (your grandma, your dog, Chick-fil-A employees). Jesus said to love your enemies and pray for those who persecute you (Matthew 5:44). That includes difficult coworkers, annoying neighbors, and even people who drive 10 miles under the speed limit in the fast lane. Keep in mind this does not give you the green light to go on loving and accepting their sins. Loving others as Christ did doesn’t mean endorsing or accepting sin. True love speaks the truth, encourages repentance, and points others toward God’s righteousness rather than affirming choices that separate us from Him.
### 8. **Be a Doer, Not Just a Hearer**
James 1:22 says, “Do not merely listen to the word, and so deceive yourselves. Do what it says.” It’s not enough to know what’s right—you have to live it. Imagine someone memorizing a cookbook but never cooking. That’s what knowing the Bible without applying it looks like.
### 9. **Trust God’s Timing**
Patience is a virtue. (And sometimes a struggle). However, a big part of living a Godly life is trusting that God’s plan is better than ours. Isaiah 40:31 says, “Those who wait on the Lord will renew their strength.” So, instead of rushing ahead, trust that God’s got the perfect timing—even when it doesn’t match your schedule.
### 10. **Laugh, Because Joy is Biblical**
Christians aren’t called to live miserable lives. In fact, Philippians 4:4 tells us to “Rejoice in the Lord always.” Yes, life gets tough. But joy in Jesus isn’t about circumstances—it’s about knowing the One who holds it all together. So, laugh, smile, and enjoy the blessings God has given you.
### **Final Thoughts**
Living a Godly life isn’t about perfection—it’s about direction. You’ll stumble, you’ll mess up, and you’ll occasionally say things you immediately regret. But God’s grace is bigger than our failures. Keep seeking Him, keep walking in His ways, and remember: the goal isn’t to be “good enough”—it’s to be faithful.
And if you ever feel discouraged, just remember: even Peter walked on water…until he looked down, became afraid, and started sinking. He cried out to the Lord, and Jesus immediately lifted him back up to safety. Keep your eyes on Jesus; Rely on Jesus for everything, and you’ll be just fine.
-

@ 8f69ac99:4f92f5fd
2025-04-01 15:54:53
Bitcoin tem-se afirmado como um meio de pagamento global, [atraindo cada vez mais comerciantes](https://btcmap.org/map#7/40.24180/-7.05872) e consumidores. Em Portugal, os pequenos e médios empresários têm uma oportunidade única para reduzir custos, expandir mercados e proteger-se da inflação ao aceitar bitcoin como opção pagamento.
Apesar das vantagens, muitos comerciantes enfrentam desafios significativos, especialmente no que toca às obrigações fiscais e à falta de conhecimento (ou vontade de aprender) por parte dos contabilistas. Questões como o registo contábil adequado, a tributação do IRC e a facturação com IVA ainda geram incerteza e dificultam a adopção da criptomoeda.
Este artigo explora como os comerciantes podem aceitar bitcoin de forma legal e eficiente, analisa os desafios fiscais e contábeis e apresenta soluções práticas para superar os obstáculos impostos pela regulamentação e pela falta de apoio dos profissionais de contabilidade.
## Benefícios de Aceitar Bitcoin
### 1. Redução de Custos
Aceitar pagamentos em bitcoin permite evitar taxas bancárias elevadas, especialmente em transacções internacionais. Como as transferências ocorrem directamente entre carteiras digitais, **sem a intermediação de bancos**, os comerciantes podem poupar significativamente em comissões e taxas de processamento.
### 2. Liquidação Rápida
Diferente dos pagamentos bancários tradicionais, que podem demorar dias, uma transacção na rede Bitcoin pode ser confirmada em minutos, ou em segundos ou menos usando a Lightning Network. Isto reduz o tempo de espera para a disponibilidade dos fundos e melhora o fluxo de caixa dos comerciantes.
### 3. Expansão de Mercado
Os comerciantes podem atrair clientes internacionais e um público mais inovador e tecnológico. A aceitação de bitcoin pode diferenciar um negócio da concorrência e aumentar a base de clientes ao incluir entusiastas de criptomoedas e consumidores que preferem meios de pagamento descentralizados.
### 4. Protecção Contra Inflação
Bitcoin pode actuar como reserva de valor, protegendo o património contra desvalorizações monetárias. Em contextos de inflação elevada, manter parte do capital em Bitcoin pode ajudar a preservar o poder de compra a longo prazo.
| [](https://youtu.be/B9fCDjybtrU&t=3518) |
|:--:|
| *Bruno de Gouveia da Care to Beauty - A Seita Bitcoin* |
## Como Funciona na Prática?
### 1. Aceitação Directa vs. Conversão Automática
Os comerciantes podem optar por aceitar bitcoin directamente, mantendo-o na sua carteira digital, ou utilizar serviços como OpenNode, Swiss Bitcoin Pay, Coincorner ou Coinbase para converter automaticamente os pagamentos em euros. A escolha depende da estratégia da empresa quanto à exposição à volatilidade da criptomoeda.
### 2. Configuração de Carteira Bitcoin
Para receber pagamentos directamente, o comerciante precisa de uma carteira Bitcoin segura, como Electrum, BlueWallet ou Aqua entre outras. Estas carteiras oferecem diferentes níveis de segurança e acessibilidade, permitindo que os comerciantes escolham a solução mais adequada ao seu modelo de negócio.
### 3. Facturação e Registo Contábil
Cada pagamento deve ser facturado em euros, com referência à taxa de câmbio do momento. O registo contábil deve ser feito correctamente para garantir a conformidade fiscal, reflectindo o valor recebido em bitcoin e a sua equivalência em euros na altura da transacção. Muitas carteiras e plataformas de pagamento oferecem relatórios detalhados que facilitam o registo contábil e a declaração fiscal.
## Obrigações Fiscais e Contábeis
### 1. IRC (Imposto sobre o Rendimento das Pessoas Colectivas)
Os rendimentos obtidos através de bitcoin devem ser devidamente registados na contabilidade da empresa, uma vez que são considerados receitas operacionais. Para efeitos fiscais, a conversão do valor recebido em bitcoin deve ser feita com base na taxa de câmbio vigente no momento da transacção, garantindo um registo transparente e conforme com as normas contábeis.
Se a empresa optar por manter os bitcoins sem os converter imediatamente para euros, estes podem ser classificados como activos intangíveis, conforme a Norma Contabilística e de Relato Financeiro (NCRF), artigo 6. No entanto, se forem utilizados como meio de pagamento recorrente, por exemplo pagar a fornecedores que também aceitem bitcoin, podem ser classificados como inventário, dependendo da natureza da actividade empresarial.
No momento da venda ou conversão dos bitcoins para euros, qualquer mais-valia obtida é considerada um rendimento da empresa e estará sujeita a tributação em sede de IRC à taxa geral em vigor.
### 2. IVA (Imposto sobre o Valor Acrescentado)
As transacções de troca de bitcoin por euros estão isentas de IVA, conforme o artigo 9.º, alínea 27), subalínea d), do Código do IVA (CIVA), que reconhece as criptomoedas como meios de pagamento e as exclui da incidência de IVA.
No entanto, a venda de bens ou serviços pagos em bitcoin deve ser facturada normalmente, em euros, com a taxa de IVA correspondente ao produto ou serviço comercializado. Para garantir conformidade fiscal, a factura deve indicar a contrapartida em euros, com base na taxa de câmbio do momento da transacção, independentemente da moeda utilizada no pagamento.
**Na prática**, aceitar pagamento em bitcoin funciona de forma muito semelhante a aceitar pagamento em dinheiro físico... 😉
### 3. Registos e Demonstrações Financeiras
As empresas que aceitam bitcoin devem manter registos contabilísticos detalhados sobre todas as transacções realizadas. bitcoin pode ser registado como activo intangível ou inventário, dependendo do seu uso:
- **Activo intangível:** Quando a empresa detém bitcoin como reserva de valor ou investimento, registando-o ao custo de aquisição e procedendo a ajustamentos caso haja desvalorização relevante.
- **Inventário:** Se a empresa opera no sector de compra e venda de criptomoedas ou usa bitcoin para transacções comerciais frequentes, deve ser registado como inventário, seguindo as regras de mensuração aplicáveis a mercadorias.
As demonstrações financeiras devem reflectir correctamente a posse de bitcoin, incluindo informações sobre variações de valor ao longo do tempo. Os contabilistas devem garantir a correta apresentação destes activos nos balanços e relatórios anuais, o que pode exigir reavaliação periódica dos valores contabilizados.
## O Obstáculo: Contabilistas e a Falta de Apoio
### 1. Falta de Conhecimento
Muitos TOC não estão familiarizados com a contabilidade de criptomoedas, o que gera incertezas e complicações para os comerciantes.
### 2. Resistência e Falta de Vontade
Em vez de se actualizarem, muitos contabilistas recusam-se a aprender sobre Bitcoin, deixando os comerciantes sem apoio adequado.
### 3. Impacto nos Negócios
Com a falta de informação e apoio dos TOC, muitos comerciantes evitam aceitar bitcoin, perdendo uma oportunidade de mercado.
## Soluções e Alternativas
### 1. Educação e Autonomia
Os comerciantes podem aprender o essencial sobre contabilidade de bitcoin para questionar e orientar os seus contabilistas. Existem recursos online, cursos e materiais educativos que permitem aos empresários compreender as melhores práticas para registo e declaração das transacções em bitcoin.
### 2. Ferramentas e Software
Existem algumas plataformas que ajudam na gestão e declaração de criptomoedas, fornecendo relatórios detalhados sobre transacções, ganhos e impostos devidos. Essas ferramentas facilitam a organização financeira e reduzem erros contábeis.
### 3. Rede de Apoio
Juntar-se a comunidades de empresários e especialistas em bitcoin pode ajudar a encontrar soluções e recomendações de contabilistas competentes. Fóruns, grupos em redes sociais e associações focadas no tema podem ser excelentes fontes de suporte e partilha de experiências.
### 4. Links uteis
- [Website Aceita Bitcoin](https://aceitabitcoin.pt)
- [Grupo Telegram Aceita Bitcoin](https://t.me/aceitabitcoin)
- [Mario Moura Contabilidade](https://mmc.pt/en/)
- [MM Law](https://www.mmlaw.pt/)
## Conclusão
Aceitar bitcoin pode ser vantajoso para pequenos e médios comerciantes, mas a burocracia e a falta de conhecimento dos contabilistas dificultam esse processo. É essencial que os comerciantes exijam um melhor serviço dos seus TOC e procurem alternativas para garantir que estão em conformidade com a lei, aproveitando ao mesmo tempo os benefícios desta nova forma de pagamento.
---
_**Disclaimer:** Este artigo é meramente informativo e não deve ser considerado como aconselhamento jurídico ou fiscal. É recomendável consultar um profissional qualificado para obter orientações específicas sobre a aceitação de bitcoin e as obrigações fiscais associadas. A legislação pode variar e é importante estar sempre actualizado com as normas vigentes. A responsabilidade pela aceitação de bitcoin e o cumprimento das obrigações fiscais recai exclusivamente sobre o comerciante. O autor não se responsabiliza por quaisquer consequências decorrentes da aceitação de bitcoin ou da interpretação das informações contidas neste artigo._
_Photo by [CardMapr.nl](https://unsplash.com/@cardmapr?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash) on
[Unsplash](https://unsplash.com/photos/black-samsung-android-smartphone-on-brown-wooden-table-rDzI7m7sjPE?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash)_
-

@ 0d1702d6:8f1ac66f
2025-04-01 15:33:09
**"Die Russen kommen..." - oder kommen sie doch nicht ?**  
 \
Hallo liebe LeserInnen und einen wunderschönen Tag miteinander!\
\
Heute allerdings sterben junge Ukrainer und Russen auch mit unserer Hilfe \
und zugleich Untätigkeit seit mehr als 168 Wochen oder 37 Monaten, mit anderen Worten also: \
seit mehr als drei Jahren, Tag für Tag, Stunde für Stunde, Minute für Minute.\
Auch in diesen Augenblicken, in denen Du dies liest...\
\
Und mit unsrer stillen Zustimmung sorgen Politiker, Medien und Waffenproduzenten \
auch unseres Landes dafür, dass das gegenseitige Abschlachten und Morden weitergeht…
**\
Die Russen kommen**…. wird uns seit 2022 im alltäglichen kriegs-propagandistischen Trommelfeuer eingehämmert, vom eher unbedarften regionalen Käseblatt bis zu den vermeintlichen Qualitätsmedien der privaten Konzerne und Staatsmedien des öffentlichen Rundfunks, dessen sich die herrschenden Parteien im Lande immer schon seit 1949 ideologisch bemächtigt haben.
100te, nein täglich tausende Male wird geschrieben, geschrien, gesagt und gedacht, suggeriert, phantasiert \
und illusioniert…oder auch nur geraunt\*\*:\*\* \
\
**die Russen kommen … und kommen und kommen …**
Zwar buddeln sich die grün hinter den Ohren frisch aufs Abschlacht-Feld gezwungenen blutig jungen Russen – und natürlich auch ihre sogenannten „Feinde“, die meist auch gegen ihren Willen zum Morden gezwungenen Ukrainer - seit über drei Jahren in den Regionen um Cherson, Donezk und Luhansk im vor allem Stellungskrieg ein, aber was solls:\
\
Morgen oder spätestens übermorgen so behauptet unser Kriegsminister und viele seiner Generäle und Geheimdienstchargen im Chor mit den Gazetten der Leitmedien: spätestens übermorgen also greifen die feststeckenden Russen dann über Nacht mit geballter Macht die jetzt-schon-Kriegspartei USA-NATO, also uns an und sichern sich sicherlich schwupp die wupp die gesamte Ukraine und dann, ja dann, geht’s sofort, also allerspätestens in vier Jahren mit voller Pulle direkt nach Berlin und Brüssel, denn \*\*„dem Russen“, dem trauen wir einfach alles wirklich Böse dieser Welt zu!\
\*\*\
Kriegsursachen, Hintergründe und Zusammenhänge wie die dutzendfach öffentlich dokumentierte und bekannte perfide US-Geostrategie Russland komplett militärisch einzukreisen und genau in die Falle zu locken, in die es reingetappt ist, haben uns noch nie interessiert, weil wir rückgratlos so tief in den Allerwertesten des imperialen Hegemons USA gekrochen sind, dass uns meist schon lange der gesunde Menschenverstand fürs Hören und Sehen, Verstehen wie Begreifen vergangen ist.
Die große Mehrheit von uns, also wir, die vermeintlich geläuterten und neuerdings pseudo-auf-geklärten Ex-Anti-Militaristen, Kriegs-Dienst-Verweigerer, paranoid schizoiden Doppel-Moral-Fetischisten der Keine-Waffen-in-KRISEN-Gebiete liefernden Grünen, also die meisten ehemals links-liberalen oder verdeckt unsozial wie unchristlich wie unfrei handelnden Demokraten der Altparteien- Einheitspartei CDU/CSU/FDP/GRÜNE/SPD & Linke (!) sitzen der Wahnvorstellung auf, die Russen würden erst die gesamte Ukraine und danach ganz Europa militärisch besetzen wollen.
**\
Du etwa nicht?** \
\
Mal im Ernst: Bist Du kein kindlich Neu-Gläubiger? Glaubst Du etwas nicht an \
„Gut“ und „Böse“ und fest daran, dass „WIR“, also „der Westen“ die Guten sind \
und „Die Russen“ - wie sicher auch „die Chinesen“ - die wirklich über alle Maßen Bösen?
Bist Du etwa doch einer dieser spät-pubertären frühzeitig dementen Alzheimeraspiranten, \
die die Lektion der russischen Revolution von 1917/1918 verdrängt, vergessen oder gar \
ge-löscht haben? Hat dir denn dein Ur-Opa nie erzählt, dass die Russen schon \
seit ihrer Oktober-Revolution 1917, ohne Quatsch, seit sage und schreibe mindestens \
108 Jahren nach Berlin marschieren und sicherlich in Kürze dort ankommen werden?
Hat Dir denn Dein Opa nie erzählt, dass diese ultra fiesen bösen Russen \
zwar unter-motorisiert, dafür aber umso mehr über-motiviert sind \
und kriegsgeil zwanghaft an ihrem Willen festhalten, \
ganz Europa zur Beute des russischen Bären zu machen??? \
\
Seit 100 Jahren zelebriert Hollywood den bösen Russen als Gegenspieler \
aller wirklich guten US-Westler. Das hat sich auch ins kollektive Bewusstsein \
der meisten Europäer tief eingegraben. 
Und bei dir?\
Sind für dich die Russen etwa keine wilden Tiere, denen wir endlich jetzt, gemeinsam \
mit dem politischen Arm des Großkapitals, also auch des militärisch-industriellen Komplexes, \
Fritzchen Merz, dem Klingbeil der abgewirtschafteten ehemals sozialen Demokraten \
und dem Steigbügelhalter der olivgrünen Kriegshysteriker unser 500 Milliarden-Plus-\
Bürger-Ermächtigungsgesetz vor sein Maul geknallt haben, sodass ihm, \
also dem russischen Bären, sehr bald Hören und Sehen vergehen wird?
Denkst Du etwa doch immer noch an den auch us-finanzierten illegalen Putsch auf dem Maidan 2014, durch den es den US-Geostrategen gelang, endlich eine us-freundliche Putschregierung in Kiew zu installieren, die dann sofort Krieg gegen die eigene russisch-stämmige Bevölkerung im Donbass führte? Denkst Du etwa immer noch an die fortschreitende und fast vollständige Umzingelung Russlands durch US-NATO-Stützpunkte, die die gutmütigen und blauäugigen Russen seit 1999 entgegen den westlichen Versprechungen jahrzehntelang geduldig ertragen haben? \
\
Bist du, ja Du, also allen Ernstes immer noch ein „Ewig-Gestriger“?\
Hast Du immer noch nicht begriffen, dass wahr ist, was 1000mal geschrieben und gesagt wurde \
und auf allen Mainstream-Medien-Kanälen seit mehr als drei Jahren auf dich einprasselt?\
\
Hast Du immer noch nicht kapiert, dass heutzutage \
**Wahrheit einfach durch Wiederholung** **\
des Falschen hergestellt** wird ???\
\
Hast Du immer noch nicht begriffen, dass es völlig zwecklos ist, dem militärisch-industriellen, \
man muss ergänzen: zugleich politisch-medialen Komplex, vor dem schon Roosevelt 1961 gewarnt hatte und wegen \
dem auch John F. Kennedy 1963 sein Leben verlor, dass es also mehr als völlig aussichtslos ist, \
dieser herrschenden gesellschaftlichen Gewaltstruktur auch nur heimlich mentalen Widerstand entgegen zu setzen?
Nun, wenn das so ist, dann liebe/r LeserIn, dann bist Du eine oder einer von uns, \
mit Sternchen versteht sich. Willkommen im Club, Wir sind viele. Viel mehr als Du vielleicht denkst. \
Denn die massenweise kapital-, parteien-, regierungs- und us-alt-establishment-nah \
**veröffentlichte Meinung ist noch lange nicht** **die öffentliche Meinung.**
Will sagen: Es gibt eigentlich keine bürgerliche Mehrheit für diese Kriegskredite von 2025. \
Sie wurden durch Lug und Trug einer schon abgewählten Parlaments-Mehrheit erschlichen. \
Die SPD hat in 111 Jahren seit ihrem Votum für Welt-Kriegskredite 1914 nichts, \
aber auch gar nichts dazu gelernt, die Oliv-Grünen haben alles, aber auch alles über Bord geworfen, \
für das sie mal – auch übrigens durch meine minimale Mithilfe – gegründet wurden….\
und die un-christlichen „C“ Parteien tun das, was ihre Vorläufer schon 1933 getan haben, \
wohlweislich heutzutage unter anderem Namen: \
dem Krieg zu den Waffen verhelfen, die Krieg nun mal braucht.
\
Wenn ich nachts an Deutschland denken würde, wäre ich um meinen Schlaf gebracht.\
Ich denke aber nicht an Nationen, ich denke an Menschen. An hunderttausende junge Menschen, \
die durch sogenannte parlamentarische Demokraten mit "Made in Germany \
and USA Waffen" in den Tod getrieben werden.
\*\*Nicht in meinem Namen. Und ich hoffe: Auch nicht in Deinem.\
\*\*\
Seit 2014 hätte ehrlich verhandelt werden müssen, heute muss es mehr denn je sofort. \
Denn die berechtigten Sicherheitsinteressen aller Nationen Europas, \
der ehemaligen Staaten der UDSSR wie auch Russlands selber können \
**nur in einem Sicherheitssystem für ganz Europa,** \
**vom Atlantik bis hinter den Ural**, Richtung Frieden verhandelt werden. \
\
Waffen ermöglichen und befeuern das Erpressen & Morden, für Frieden sind sie ungeeignet.
**Sicherheit ist unteilbar: Sicherheit & Frieden gibt es nur für alle, oder für keinen.**
-

@ f1989a96:bcaaf2c1
2025-04-01 14:31:43
**NEW YORK** (April 1,2025) — The Human Rights Foundation (HRF) is pleased to announce 1 billion satoshis of gifts from its [Bitcoin Development Fund](https://hrf.org/devfund). HRF’s latest batch of grants supports open-source development, educational initiatives, mining decentralization, and privacy tools for activists living under authoritarian regimes across Latin America, Africa, and Asia. The gifts also further promote Internet freedom and decentralized communications, ensuring dissidents can connect, communicate, organize, and transact without censorship.
Quarter 1 2025 grantees include:
- **NetBlocks**
Authoritarian regimes weaponize Internet shutdowns to silence dissent, restrict information, and cut off financial lifelines. By blocking communication channels, they isolate individuals, suppress independent media, and disrupt financial flows. [NetBlocks](https://netblocks.org/) exposes these digital crackdowns in real time, ensuring the world sees and responds to digital repression. Through continuous monitoring, it equips activists, journalists, and civil society with the data needed to challenge censorship and advocate for an open internet. With HRF support, NetBlocks will expand its monitoring, documentation, and research — reinforcing internet and financial freedom as a critical human rights safeguard.
- **TollGate**
Authoritarian regimes exploit Internet Service Providers (ISPs) to monitor and suppress dissent, undermining online privacy essential for human rights defenders. [TollGate](https://opentollgate.github.io/tollgate/), developed by c03rad0r, is software that transforms any WiFi router into a permissionless Internet Service Provider (ISP) using Bitcoin and ecash. By decentralizing Internet access and turning any WiFi router into part of a peer-to-peer, private, open internet network, Tollgate helps resist authoritarian surveillance and protect digital freedoms. With HRF support, TollGate is advancing an open, accessible, and censorship-proof internet for those who need it most.
- **Vinteum**
Across Latin America, authoritarian regimes restrict financial access to tighten their grip on power. But a growing network of developers is working to change that. [Vinteum](https://vinteum.org/), a nonprofit Bitcoin research and development center led by executive director [Lucas Ferreira](https://x.com/lucasdcf), trains and funds developers to strengthen Bitcoin as a tool for financial freedom. Through education, development, and community building, Vinteum fosters local talent and expands regional Bitcoin accessibility. With HRF support, Vinteum will scale its programs and help more Latin Americans achieve financial independence.
- **BTCPay Server**
Dictators often block payment processors to cripple the work of nonprofits and dissidents. [BTCPay Server](https://btcpayserver.org/), a self-hosted, open-source Bitcoin payment processor, now breaks this control. It provides individuals, nonprofits, and merchants with a censorship-resistant way to accept payments. Activists and nonprofits can now process global payments, launch crowdfunding campaigns, and build movements on Bitcoin — all without third parties or restrictions. With HRF support, BTCPay Server will expand access to self-custodial payments, enabling more organizations under dictatorships to transact freely.
- **Africa Bitcoin Institute (ABI)**
Across Africa, dictators manipulate financial institutions to retain control, while more than half the population remains unbanked. Bitcoin offers an alternative, but without proper research, education, and policy frameworks, adoption remains limited. The Africa Bitcoin Institute (ABI), supported by the Rwandan human rights activist [Anaïse Kanimba](https://x.com/AnaiseKanimba), is launching to bridge this gap. Through evidence-based research and policy recommendations, ABI will equip policymakers with the knowledge and tools to integrate Bitcoin into African economies. With HRF support, ABI will promote financial autonomy and solidify Bitcoin’s role as a pillar of economic freedom.
- **Bitcoin Core Graphical User Interface**
Running a Bitcoin node (software that enables users to verify transitions and enforce the network’s rules) is key to financial sovereignty. But outdated and clunky interfaces make it difficult, especially on mobile devices. [bitcoin-core/gui-qml](https://github.com/bitcoin-core/gui), a project [Go Qu](https://github.com/goqusan) will contribute to, modernizes Bitcoin Core’s interface to be more accessible and mobile-friendly. By lowering the barriers to node operation, this project empowers more people — especially under autocracies in Africa, where mobile phones dominate — to strengthen their financial sovereignty. With HRF support, bitcoin-core/gui-qml is expanding node access, supporting Bitcoin’s decentralization, and reinforcing its censorship resistance for the long term.
- **Rkrux**
As an open-source project, Bitcoin Core relies on free and open-source developers to maintain its integrity, security, and resilience against potential threats. [Rkrux](https://github.com/rkrux), a Bitcoin Core developer, plays a crucial role by reviewing code, testing releases, and improving documentation to keep Bitcoin Core robust, secure, and censorship-resistant. Rkurx’s work identifies vulnerabilities, refines changes, and strengthens Bitcoin’s long-term stability. With HRF support, Rkrux is deepening his contributions, reinforcing Bitcoin’s foundation, and ensuring it remains a financial lifeline for human rights defenders worldwide.
- **Elsat**
As online censorship intensifies, free speech and financial freedom are under threat. Nostr developer [Elsat](https://github.com/alltheseas) is working to defend these freedoms by contributing to [Damus](https://github.com/damus-io), [Nostrability](https://github.com/nostrability), and [Zap.store](https://github.com/zapstore) — projects that empower individuals to communicate and transact without centralized control. Damus enables private, censorship-resistant messaging; Nostrability improves app interoperability; and Zap.store helps free and open-source software (FOSS) developers distribute and monetize their work peer-to-peer. With HRF support, Elsat is strengthening tools that protect free speech for dissidents under oppressive environments.
- **Relay Wizard**
Nostr, a decentralized communication protocol, relies on a network of relays (servers that pass messages between users). But setting up relays can be complex and intimidating. [Relay Wizard,](https://github.com/nodetec/relaywizard) a tool created by software developer [J the Code Monkey](https://github.com/jchiarulli), simplifies this process by automating relay setup. This allows anyone to run a relay, reduces reliance on intermediaries, and helps keep nostr resilient against online speech censorship. With HRF support, J the Code Monkey will expand development and operations, ensuring nostr remains a secure, uncensorable communication platform accessible to everyone.
- **Waye**
Censorship-resistant technology is essential to protecting global freedom. Yet open-source developers often operate like solo entrepreneurs — juggling engineering, project management, and community-building on their own. This leads to inefficiency, isolation, and burnout. [Waye](http://waye.dev) addresses this gap by providing psycho-social support for developers working on freedom tech. Led by Bitcoin Core developer Amiti Uttarwar and operational architect Anna Sides, Waye strengthens the human infrastructure of open source. With HRF support, Waye will support developers from global majority countries, empowering them to build the tools their fellow citizens need.
- **Hashpool**
Centralization in Bitcoin mining threatens its censorship resistance and makes it harder for small-scale miners to compete. [Hashpool](https://github.com/vnprc/hashpool), a self-hosted mining pool by developer [vnprc](https://github.com/vnprc), eliminates reliance on centralized entities while giving miners more control over their earnings. Instead of traditional mining pool payouts, Hashpool rewards participants with ecash tokens — digital cash that enables instant, private transactions. This ensures miners receive payouts instantly while preserving their financial privacy. It also helps keep mining open and decentralized. With HRF support, vnprc will further develop Hashpool and help resist mining centralization.
- **Cashu KVAC**
As dictators ramp up financial surveillance to threaten dissidents, protecting financial privacy is more critical than ever. [Cashu KVAC](https://github.com/lollerfirst/cashu-kvac) is a software upgrade for Cashu — a Chaumian ecash-based system that enables extremely strong financial privacy. Developed by [lollerfirst](https://github.com/lollerfirst), it improves privacy and efficiency by reducing wallet data storage and concealing transaction amounts from third parties. These improvements strengthen ecash functionality, safeguarding financial privacy for individuals and nonprofits alike. With HRF support, lollerfirst will develop Cashu KVAC and help protect digital and financial freedom for those living under the watchful eyes of dictators.
- **Self-Custody Research**
In unstable economies and under authoritarian regimes, self-custodial Bitcoin is a financial lifeline — portable money that cannot be seized, censored, or debased. While Bitcoin enables financial freedom, scaling self-custody remains a challenge. Bitcoin educator and developer [Brandon Black](https://github.com/reardencode) (Rearden) is researching these limitations and exploring technical solutions to make self-custody more accessible. His work documents the obstacles users face today and provides insights into how Bitcoin can evolve. With HRF support, Black will expand self-custody education, equipping individuals under dictatorships with the knowledge and tools to secure their financial independence.
- **Stable Channels**
For citizens living under authoritarian regimes and struggling economies, Bitcoin is a lifeline — but its volatility can threaten short-term financial security. [Stable Channels](https://github.com/toneloc/stable-channels/), created by software engineer [Tony Klausing](https://tonyklausing.com/), brings stabilized Bitcoin-backed balances to the Lightning Network (allowing users to peg Bitcoin to fiat currencies in a self-custodial way). This innovation enables individuals to transact freely without exposure to wild price swings or to centralized stablecoins. HRF’s support will help expand Stable Channels development, ecash integrations, and community outreach — helping more individuals harness Bitcoin’s power while maintaining financial stability.
- **Bitsacco**
In Kenya, Savings and Credit Cooperative Organizations (SACCOs) provide savings and lending services to their communities. But reliance on traditional banks limits their autonomy. [Bitsacco](https://github.com/bitsacco/os), created by developer [okjodom](https://github.com/okjodom), reinvents SACCOs by leveraging Bitcoin and Fedimints (a community-based custody model in Bitcoin). In this way, Bitsacco offers a more open, inclusive, and self-sustaining financial option. By reducing dependence on banks, Bitsacco empowers communities to manage their savings and loans independently. With HRF support, Bitsacco will provide a secure, familiar path to sound money in a region where financial instability and restricted access are persistent challenges.
- **The Core**
In Africa, where financial literacy gaps persist, hands-on Bitcoin education is crucial for adoption. [The Core](https://github.com/thecore21m-btc), founded by Kenyan Bitcoin educator [Felix Mukungu](https://x.com/MukunguFelix), bridges this gap by equipping Africans with the knowledge and skills to use Bitcoin confidently. Through hands-on training in self-custody, Lightning wallets, and Bitcoin nodes, The Core empowers individuals to take control of their money and transact freely. This grant will help expand The Core’s monthly meetups, online courses, and student-support programs — bringing Bitcoin education to more individuals across Kenya and the wider African continent.
- **Bitcoin Babies**
Under many authoritarian regimes, infant malnutrition is exacerbated and puts countless children at risk. [Bitcoin Babies](https://bitcoinbabies.com/), founded by [Naomi Wambui](https://x.com/NgachaNaomi1), is a project that tackles this issue by combining infant nutrition education with Bitcoin-based financial literacy. Through weekly Bitcoin stipends, financial literacy training, and community support, mothers under authoritarian rule gain the tools needed to improve their children’s health while achieving long-term financial stability. With this grant, Bitcoin Babies will expand its impact, helping more at-risk communities with resources that are otherwise unavailable and inaccessible, empowering mothers to build brighter futures.
- **East Asia Bitcoin Developer Apprenticeship Program**
In East Asia, language barriers and limited mentorship have made open-source Bitcoin development inaccessible to many. The [East Asia Bitcoin Developer Apprenticeship Program](https://x.com/kcalvinalvinn), led by Bitcoin developer [Calvin Kim](https://x.com/kcalvinalvinn), is changing that by creating a pathway for Korean and Japanese developers to enter the field. Through hands-on training, mentees gain practical experience, contribute to open-source projects, and eventually become mentors — strengthening the region’s developer ecosystem. With this funding, the apprenticeship program will expand, diversify Bitcoin’s global developer base, make freedom technology more accessible across Asia, and forge links with North Korean defectors.
- **Bitcoin Week at TalentLand 2025**
Across Latin America, government overreach threatens financial freedom. At [TalentLand 2025](https://talent-land.mx/), Latin America’s largest tech event, Bitcoin Week will demonstrate how Bitcoin empowers individuals to reclaim their financial sovereignty. Led by developer [Super Testnet](https://github.com/supertestnet) and the Bitcoin and Lightning Guadalajara community, this initiative educates Mexico’s tech community on Bitcoin’s role in fostering financial sovereignty. Through workshops, hackathons, and debates, it nurtures developer talent and engages future tech leaders. With this funding, Bitcoin Week will help expand awareness of Bitcoin’s power to resist financial oppression and accelerate Bitcoin adoption across Latin America.
- **Base58**
Learning Bitcoin’s technical aspects can feel overwhelming. [Base58’s Bitcoin Live Action Role Play](https://github.com/base58btc/LARP) (LARP) simplifies this with a two-hour workshop where participants act out the Bitcoin network and see how transactions are made, how they get to miners, the work a Bitcoin node does, and how it helps secure the network. Created by [Lisa Neigut](https://x.com/niftynei) (niftynei), a prolific Bitcoin developer, educator, and founder of [Base58](https://base58.school/) and the [bitcoin++](https://btcplusplus.dev/) conference, alongside David Rodriguez, this immersive experience makes Bitcoin education tangible and entertaining. Now expanding beyond North America, it will train new facilitators, prioritizing regions with limited Bitcoin education due to authoritarian restrictions. With this funding, Base58 Bitcoin LARP will equip more facilitators to teach and learn Bitcoin in an engaging, accessible way.
- **BTCenEspañol**
Across Latin America, financial repression and limited access to Bitcoin education leave many without the tools to navigate financial repression. [BTCenEspañol](https://www.btcenespanol.com/) has been a leader in Spanish-language Bitcoin education since 2014. With a goal of reaching one million learners and training 100 teachers, BTCenEspañol is expanding to make Bitcoin education more accessible across the region, especially in places like Nicaragua and Venezuela. HRF’s grant will support this growth, equipping individuals with the knowledge to secure their financial independence amid rising authoritarianism in the continent.
- **Increasing nonprofit Adoption of Bitcoin**
Under dictatorships, non-governmental organizations face frozen bank accounts, surveillance, and financial censorship — limiting their ability to support vulnerable communities. Bitcoin researcher [Daniel Batten](https://x.com/dsbatten) is quantifying Bitcoin’s role as a financial lifeline to help nonprofits overcome these challenges. Through empirical research, his initiative will show how Bitcoin enables nonprofits under authoritarian regimes to operate more freely. With this grant, the project will equip nonprofits in closed societies with the knowledge and tools to integrate Bitcoin into their operations, strengthening their financial resilience and advancing global movements.
- **Bitcoin for Good**
When authoritarian regimes weaponize the financial system against dissent, nonprofits and charities are among the first to suffer. Bitcoin for Good is an educational initiative led by activist and Groundswell founder [Hadiya Masieh](https://www.groundswellproject.org/about/who-we-are/). It helps organizations break free by teaching them how to accept and manage censorship-resistant funding. Through hands-on training and direct integration with Bitcoin for donations, nonprofits learn to operate outside the reach of financial gatekeepers and regimes. With this grant, Bitcoin for Good will help nonprofits stay funded, independent, and free to continue their work.
About BDF HRF’s Bitcoin Development Fund (BDF) supports individuals and projects that make Bitcoin and related freedom technologies more powerful tools for human rights defenders operating in challenging political and financial environments. Since launching in 2020, BDF has gifted $7.8 million in BTC to 284 projects across 62 countries worldwide. The next round of grants will be announced at the 17th annual Oslo Freedom Forum, taking place May 26-28, 2025, in Oslo, Norway.
Learn more about HRF’s Bitcoin Development Fund on our website.
### About BDF
HRF’s Bitcoin Development Fund (BDF) supports individuals and projects that make Bitcoin and related freedom technologies more powerful tools for human rights defenders operating in challenging political and financial environments. Since launching in 2020, BDF has gifted $7.8 million in BTC to 284 projects across 62 countries worldwide. The next round of grants will be announced at the [17th annual Oslo Freedom Forum](http://oslofreedomforum.com), taking place May 26-28, 2025, in Oslo, Norway.
Learn more about HRF’s Bitcoin Development Fund on our [website](https://hrf.org/program/financial-freedom/bitcoin-development-fund/).
*HRF is a registered 501(c)(3) nonprofit organization. Donations are tax-deductible to the fullest extent allowable by law. Gifts can be made at [HRF.org/DevFund](https://hrf.org/devfund), and proposals for support can be submitted to [https://hrf.org/bdfapply](https://hrf.org/bdfapply).*
*Follow [@HRF](https://twitter.com/HRF) on X for more updates on this project and all of our other programs designed to promote freedom and human rights around the world.*
-

@ 5d4b6c8d:8a1c1ee3
2025-04-01 13:41:45
I'm trying out a new month-long focus. For Active April, I'm going to be more proactive about doing stuff around the house that needs doing.
It's gonna get all Jordan Peterson cleaning your room up in here. Let's see how noticeable the consequences are.
- I predict a happier wife, for one.
- I'm also curious to see what kind of fitness impacts there are to increasing this kind of activity, compared to doing more exercise.
originally posted at https://stacker.news/items/931099
-

@ fd78c37f:a0ec0833
2025-04-01 11:49:06
In this edition, we invited Keypleb, the founder of Bitcoin Indonesia, to share how he built the Bitcoin community in Indonesia, overcoming challenges like member turnover and venue selection, while driving the adoption and growth of Bitcoin.
**YakiHonne**: Welcome, Keypleb. Before we begin, let me briefly introduce YakiHonne. YakiHonne is a decentralized media client built on Nostr—a protocol designed to empower freedom of speech through technology. It enables creators to own their voices and assets while offering innovative tools like smart widgets, verified notes, and support for long-form content. We focus on free speech and free media by user privacy and data to be protected. So before starting the interview, I'd like to hear about yourself and your community.
**Keypleb**:My name is Keypleb, though it’s a pseudonym—a name I use to respect privacy. I'm a co-founder of Bitcoin Indonesia, Bitcoin House Bali, and Code Orange, a new developer school we launched at a conference just a few days ago. We focus on driving adoption through meetups, hackathons, and technical workshops. I'll dive into more details later, but that's a brief overview. I'm based in Bali now, though I travel a lot and consider myself quite nomadic. Great to be here.
**YakiHonne**: What sparked your interest in Bitcoin and what motivated you to create a community on Bitcoin?
**Keypleb**:I first got interested in Bitcoin because it solved a specific problem. At the time, I didn’t know exactly what the solution was, but the problem was that I couldn’t afford a home. Back in 2019, I was living in London, and a two-bedroom apartment was £600,000, which was insanely expensive. First-time buyers like myself simply couldn’t afford it. Why was it so expensive? Why was buying a house so hard? During the COVID lockdown, I had more time on my hands and started listening to Michael Saylor on a Bitcoin podcast, where he talked about how the system is rigged, and that’s why people work hard but still can’t afford a house. That really resonated with me. So I started looking for a community, but unfortunately, there wasn’t one..
**Keypleb**:After moving to Bali, I attended a lot of crypto meetups, especially scammy altcoin ones, thinking, “There has to be a solution.” But none of them resonated with me. There was no sense of freedom, and no real discussion about inflation resistance. I remembered a podcast from Dea Reskita, an Indonesian host who’s pretty well-known online. I reached out to her and said, “ you’ve got to help me. I’m surrounded by all these shitcoiners, and I can’t take it anymore. I need a real community. Is anything happening?” She replied, “Yes, something is happening. We should restart these meetups next month.” And that’s how it all began.
**Keypleb**:There’s also another story about how we started Bitcoin House and how Bitcoin in Asia came to be, but maybe I’ll save that for later. Anyway, the spark of interest came from Bitcoin solving a real problem, and my drive to keep going came from the lack of quality meetups. Now, we’ve hosted 31 meetups, launched Bitcoin House and Code Orange, and the movement is growing rapidly.

**YakiHonne**: That’s such an amazing story—going from being on the brink of homelessness to creating something so impactful, and keeping it running every day, bringing new people into the journey. It’s truly inspiring. I’m curious about how the community started. How did you manage to attract members and build a strong community? What challenges did you face along the way?
**Keypleb**:It all started with our first meetup at the end of 2022, which was two and a half years ago now. At that time, we sent out an email to a group from a previous database, and the first meetup had around 20 people, which was a good start. However, problems quickly arose as people started dropping off, and the community lacked retention. In Bali, people come and go, usually staying for no more than two months, leading to a lack of long-term participation. This became one of our challenges: how to attract more people and, more importantly, get the same people to keep coming back. While I've been coming back for two and a half years, not everyone is able to return as often, and that has been a real challenge.
**Keypleb**:Actually, I should also mention how I met my co-founders—Marius, Diana, and Dimas. We met at the 2023 Indonesia Bitcoin Conference. As time went on, we kept hosting meetups and had a lot of fun each time, though the locations kept changing. One of the initial challenges was that we didn't realize the importance of having a fixed meetup location. We changed venues several times before we realized that having a consistent location is crucial. If anyone wants to run a meetup, it's best to always choose a fixed location. We learned this through trial and error, but now it's no longer an issue.
**Keypleb**:Since the conference, my co-founders and I have been working together, consistently putting in the effort. This is why our community has grown so large—so far, we are hosting 31 monthly meetups, 6 of which are in Bali. This means there is a bitcoin meetup almost every day on a regular basis. We've also established Bitcoin House Bali, a physical space, and the movement is growing rapidly. Without this movement, the region would face many challenges, including inflation and heavy censorship. It all started from just one meetup.

**YakiHonne**: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now?
**Keypleb**:First, one very important piece of advice is to ensure that every meetup is held at the same location regularly. We realized this challenge through trial and error. To help others who are interested, we’ve published our meetup guide on GitHub, where everyone can check it out. For example, meetups should be held regularly, ideally once a month, or even once a week. In Chiang Mai, the Bitcoin meetup starts every Thursday at 7 PM, and everyone knows the time and location, making it easy to join without having to look up the next meetup.
**Keypleb**:Additionally, our meetup structure is very simple. First, we do a round of introductions where everyone shares their name, where they’re from, and what Bitcoin means to them. This usually takes about 15 minutes. Then, we discuss three main questions: First, why do we need Bitcoin? The discussion typically focuses on two main issues Bitcoin addresses: inflation and censorship;Secondly, how to buy Bitcoin? We usually ask who wants to buy some Bitcoin, and then we do a small purchase together and conduct a P2P trade to demonstrate how easy it is to buy Bitcoin. Lastly, how to store Bitcoin? We introduce self-custody and show how to use hardware wallets (like Trezor), explaining the concept of the 12 words and private keys.
**Keypleb**:The whole meetup usually wraps up in about an hour, after which people can continue socializing at Bitcoin House or wherever the meetup is taking place. In short, keeping the meetup simple and efficient, and ensuring a fixed location for each event, are key factors in building a successful community.
**YakiHonne**: What's the major approach? Is it more technical, or do you focus on non-technical aspects, or do you cover both?
**Keypleb**:Our approach includes both technical and non-technical content. Initially, our meetups were completely non-technical, just casual gatherings for people to socialize. Over time, however, we've evolved to incorporate more technical content.
**Keypleb**:Out of the 31 monthly regular meetups we host, most of them have been non-technical, simply regular gatherings held at the same time and place according to our meetup guide. For example, we host the “Bitcoin for Beginners” meetup, which is designed for newcomers and takes place every second Friday of the month at 5 PM at the Bitcoin House Bali. This is entirely non-technical. Additionally, every Wednesday at Bitcoin House, we host the “My First Bitcoin” course. While the course touches on some technical aspects, such as seed phrases and backups, it’s still beginner-friendly and not too technical. The course runs for 10 weeks, and we plan to offer it in the local language at Bali University to help the local community better understand Bitcoin.
**Keypleb**:On the other hand, we also offer highly technical content. We launched a new program called “Code Orange,” which is specifically designed for developers and programmers. We use the “Decoding Bitcoin” website, created by Jamal, which is a learning platform for developers. Many developer schools, like Code Orange, use this resource. Additionally, we host “Code Orange” meetups where we dive into the technical aspects of Bitcoin, such as how mining works and how to prevent single points of failure.
**Keypleb**:We also organize technical workshops, such as “How to Defend Against a Five-Dollar Wrench Attack,” which is closely related to security. Recently, there have been some kidnapping incidents in Bali, and many people are concerned about their Bitcoin being stolen. To address this, we plan to hold a workshop on how to protect Bitcoin against such attacks. Additionally, we host hackathons and other high-tech events, and we just completed a very successful beginner-level hackathon.
**Keypleb**:In summary, our community caters to everyone, from beginners to technical experts. For beginners, we offer easy-to-understand, non-technical content, while for experienced Bitcoiners, we provide in-depth technical material.

**YakiHonne**: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved?
**Keypleb**:I have some additional advice. First, technical individuals can sign up for the “Decoding Bitcoin” course that starts on 18th March 2025 or join our “Code Orange” program and participate in the end-of-year hackathon. If they are technically proficient, this will be a great opportunity. “Decoding Bitcoin” is great for beginners, but it’s also useful for technical individuals. If someone is very skilled, they can start contributing code right away. If they find the course too easy, they can skip it and dive directly into more advanced projects. Additionally, Bitshala and Chaincode Labs offer advanced courses, which more technically advanced individuals can choose to pursue.

**Keypleb**:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash.
**YakiHonne**: I’d like to move on to the next question: How do you see Bitcoin communities evolving as technology progresses, particularly in areas like scalability, privacy, and adaptability to other systems?
Keypleb:I believe the Bitcoin community will continue to evolve, and it has already made incredible progress. Two and a half years ago, we started alone in Bali, with just ourselves. We began in the official phase and have had numerous conversations throughout the year. For example, we are now starting a Bitcoin club at a university in Bali; we just need to find a passionate, driven “Bitcoin maximalist,” and the Bitcoin club will begin. Like what our friends did in Banyuwangi, Indonesia, these clubs could eventually evolve into Bitcoin houses.
**Keypleb**:Regarding privacy and scalability, the community is making strides. We’re big fans of Fedi, which builds on top of the Fedimint protocol and uses e-cash to scale Bitcoin while improving privacy. Fedi low fees and high privacy potential give Bitcoin great opportunities in this area.
**Keypleb**:As for Bitcoin's compatibility with fiat systems, although Bitcoin payments are illegal in some countries like Indonesia, smart developers across Southeast Asia are working on legal solutions. For example, there's a website called Pleb QR that works in Thailand, allowing you to pay in fiat via the Lightning Network. Koral is another app specifically for Indonesia. These kinds of testing products already exist and are physically possible, but we’re just waiting on regulations. My influential friends are actively lobbying the government for adoption.
**Keypleb**:In summary, privacy, scalability, and compatibility with fiat systems are all works in progress, and they will continue to evolve positively. There will be more meetups, more wallet downloads, and more adoption—there’s no doubt about that.
**YakiHonne**: You mentioned the concept of cross-country issues, so I have one last question: How is the government’s stance on Bitcoin? Is the political climate supportive or against Bitcoin? How do you see the government's approach to Bitcoin in your community or environment?
**Keypleb**:This reminds me of a person, Jeff Booth, who once said, “We are them, the government is made up of us.” In Indonesia, many politicians actually support Bitcoin, and many of them mine Bitcoin themselves. When money is involved, the incentive is strong, and politicians naturally like to make more money. As a result, Indonesia has a large Bitcoin mining scene. However, overall, the Indonesian government is against Bitcoin, as seen in their ban on Bitcoin payments. The 2011 currency law states that any currency other than the Indonesian Rupiah (IDR) cannot be used, and violators can face up to one year in prison or a fine. This means you cannot pay with US dollars, lira, euros, pesos or pounds.
**Keypleb**:This shows that the government’s legal system is somewhat fragile. It’s understandable that the government is concerned about disruptive technologies like Bitcoin, especially with such a fragile fiat system. Indonesia has also seen many arrests. In 2016, Bank Indonesia issued a letter announcing a crackdown on cryptocurrency payments. Those involved in paying in Bitcoin had their funds seized, and the police cooperated in shutting down businesses accepting Bitcoin payments in the cities. While this isn't very friendly, it does highlight the fragility of the existing system. We also believe that a new executive order may be introduced in the future, similar to when President Roosevelt in 1933 ordered Americans to hand over all their gold with his Executive Order 6102. If it happened before, it could happen again.
**Keypleb**:Therefore, we predict that Bitcoin custody could become a legal issue, which is one of the reasons we blur the faces of participants at every meetup. We need to protect the community from any potential risks. But overall, we remain optimistic. Despite the government ban, the ideology of Bitcoin is unstoppable, and its spread cannot be stopped. So, we are very optimistic about the future.
**YakiHonne**: I think almost every government around the world, even in Africa, faces similar issues with Bitcoin. Some governments might want Bitcoin but hesitate to openly accept it due to the fear of it undermining the traditional financial system, which, of course, could eventually happen. But hopefully, as the new generation comes into power, we'll see more Bitcoin-friendly governments. So, thank you so much for sharing your insights and advice. I really appreciate your time and the valuable input you've provided.
**Keypleb**:I'm really glad this conversation enlightened me. I enjoyed it a lot, and it made me reflect on how much work we're doing and how valuable it is. There are a lot of problems out there, with censorship being the biggest one, followed by inflation, which is also a major issue depending on the region. But Bitcoin is open, the community is growing, and people are fighting against censorship and internet shutdowns in places like Indonesia and beyond. The movement is definitely growing. So, I'm very happy to be here and have this chat. Thanks again.
Bitcoin Indonesia nostr:
nostr:npub1y4qd2zhtn05gnsaaq5xfejzfk4a32638tx6gpp9g8k6e42g9d66qaxhcr3
Keypleb nostr:
nostr:npub190trvg63e6tyqlwlj6lccqpftx76lckj25c006vwx3dzvdl88yxs2nyqdx
-

@ 04c915da:3dfbecc9
2025-03-25 17:43:44
One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-

@ 7d33ba57:1b82db35
2025-04-01 09:17:32
Šibenik is a charming coastal town in Dalmatia, known for its stunning medieval architecture, UNESCO-listed cathedral, and scenic Adriatic coastline. Unlike many other Croatian coastal cities, Šibenik was founded by Croats (not Romans or Venetians), giving it a unique identity. It’s also the perfect gateway to Krka National Park and the Kornati Islands.

## **🏰 Top Things to See & Do in Šibenik**
### **1️⃣ St. James Cathedral (UNESCO) ⛪**
- **One of Croatia’s most impressive churches**, built entirely of **stone**.
- Features **intricate carvings** of **71 sculpted faces**, believed to be real Šibenik residents from the 15th century.
- A masterpiece blending **Gothic and Renaissance styles**, recognized as a **UNESCO World Heritage Site**.
### **2️⃣ Explore the Medieval Old Town 🏡**
- Wander through **narrow, stone-paved streets** filled with history.
- Discover hidden squares, old churches, and charming cafés.
- Stop by the **Four Wells Square**, where locals once gathered for water.

### **3️⃣ Climb to St. Michael’s Fortress 🏰**
- Offers **breathtaking panoramic views** over Šibenik and the Adriatic.
- Hosts **concerts & cultural events** in a unique open-air setting.
- One of Šibenik’s **four medieval fortresses**, well-preserved and full of history.
### **4️⃣ Visit Barone & St. John’s Fortresses 🏗️**
- **Barone Fortress** – Features an **interactive museum** and stunning **sunset views**.
- **St. John’s Fortress** – Famous for being a filming location for **Game of Thrones**.
### **5️⃣ Day Trip to Krka National Park 🌿💦**
- Just **15 minutes away**, Krka is home to **stunning waterfalls** and **lush greenery**.
- Walk the wooden pathways to **Skradinski Buk**, the park’s **largest waterfall**.
- **Boat tours** take you to **Visovac Island**, home to a historic monastery.

### **6️⃣ Boat Trip to Kornati Islands 🏝️⛵**
- A group of **89 islands**, known as the **"nautical paradise"** of Croatia.
- Ideal for **sailing, snorkeling, and exploring unspoiled nature**.
- Book a **boat tour** from Šibenik’s harbor for a day of adventure.
### **7️⃣ Relax at Banj Beach 🏖️**
- A **city beach with crystal-clear waters**, just a **short walk from the Old Town**.
- Offers stunning **views of Šibenik’s skyline and fortresses**.
- Great for swimming and sunbathing.
### **8️⃣ Enjoy Fresh Dalmatian Cuisine 🍽️**
- Try **peka** – a traditional dish of slow-cooked meat and vegetables.
- **Šibenik’s seafood** is top-notch – grilled fish, octopus salad, and black risotto.
- Pair your meal with local **Babić wine**, produced in nearby vineyards.

## **🚗 How to Get to Šibenik**
✈️ **By Air:** Nearest airports:
- **Split Airport (SPU)** – **45 min drive (60 km)**
- **Zadar Airport (ZAD)** – **50 min drive (70 km)**
🚘 **By Car:**
- **From Split:** ~1 hour (90 km)
- **From Zadar:** ~1 hour (85 km)
🚌 **By Bus:** Direct buses from **Split, Zadar, and Zagreb**.
⛵ **By Boat:** Ferries connect Šibenik to nearby islands like **Zlarin and Prvić**.

## **💡 Tips for Visiting Šibenik**
✅ **Best time to visit?** **May–September** for warm weather & outdoor festivals ☀️
✅ **Wear comfy shoes** – The Old Town’s stone streets can be steep & slippery 👟
✅ **Plan Krka trips early** – It gets busy, especially in summer 🚣
✅ **Try local olive oil & wine** – Some of Croatia’s best olive oils & wines come from Šibenik’s region 🍷🫒
✅ **Stay for sunset** – The views from St. Michael’s Fortress are unforgettable 🌅

-

@ 04c915da:3dfbecc9
2025-03-07 00:26:37
There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
**Small Wins**
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
**Ego is Volatile**
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
**Simplicity**
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
**The Big Picture**
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \
\
Stay Humble and Stack Sats. 🫡
-

@ 7d94dfe7:49219865
2025-04-01 10:31:12
Short answer: Yes
-

@ 6389be64:ef439d32
2025-02-27 21:32:12
GA, plebs. The latest episode of Bitcoin And is out, and, as always, the chicanery is running rampant. Let’s break down the biggest topics I covered, and if you want the full, unfiltered rant, make sure to listen to the episode linked below.
## House Democrats’ MEME Act: A Bad Joke?
House Democrats are proposing a bill to ban presidential meme coins, clearly aimed at Trump’s and Melania’s ill-advised token launches. While grifters launching meme coins is bad, this bill is just as ridiculous. If this legislation moves forward, expect a retaliatory strike exposing how politicians like Pelosi and Warren mysteriously amassed their fortunes. Will it pass? Doubtful. But it’s another sign of the government’s obsession with regulating everything except itself.
## Senate Banking’s First Digital Asset Hearing: The Real Target Is You
Cynthia Lummis chaired the first digital asset hearing, and—surprise!—it was all about control. The discussion centered on stablecoins, AML, and KYC regulations, with witnesses suggesting Orwellian measures like freezing stablecoin transactions unless pre-approved by authorities. What was barely mentioned? Bitcoin. They want full oversight of stablecoins, which is really about controlling financial freedom. Expect more nonsense targeting self-custody wallets under the guise of stopping “bad actors.”
## Bank of America and PayPal Want In on Stablecoins
Bank of America’s CEO openly stated they’ll launch a stablecoin as soon as regulation allows. Meanwhile, PayPal’s CEO paid for a hat using Bitcoin—not their own stablecoin, Pi USD. Why wouldn’t he use his own product? Maybe he knows stablecoins aren’t what they’re hyped up to be. Either way, the legacy financial system is gearing up to flood the market with stablecoins, not because they love crypto, but because it’s a tool to extend U.S. dollar dominance.
## MetaPlanet Buys the Dip
Japan’s MetaPlanet issued $13.4M in bonds to buy more Bitcoin, proving once again that institutions see the writing on the wall. Unlike U.S. regulators who obsess over stablecoins, some companies are actually stacking sats.
## UK Expands Crypto Seizure Powers
Across the pond, the UK government is pushing legislation to make it easier to seize and destroy crypto linked to criminal activity. While they frame it as going after the bad guys, it’s another move toward centralized control and financial surveillance.
## Bitcoin Tools & Tech: Arc, SatoChip, and Nunchuk
Some bullish Bitcoin developments: ARC v0.5 is making Bitcoin’s second layer more efficient, SatoChip now supports Taproot and Nostr, and Nunchuk launched a group wallet with chat, making multisig collaboration easier.
## The Bottom Line
The state is coming for financial privacy and control, and stablecoins are their weapon of choice. Bitcoiners need to stay focused, keep their coins in self-custody, and build out parallel systems. Expect more regulatory attacks, but don’t let them distract you—just keep stacking and transacting in ways they can’t control.
**🎧 Listen to the full episode here: [https://fountain.fm/episode/PYITCo18AJnsEkKLz2Ks](Fountain.fm)**
**💰 Support the show by boosting sats on Podcasting 2.0!** and I will see you on the other side.
-

@ e373ca41:b82abcc5
2025-04-01 08:44:15
***
*This article first appeared in German at* ***[Freischwebende Intelligenz.](https://www.freischwebende-intelligenz.org/p/an-der-zeitmauer-der-entblindung)*** *You can find all the articles by Free-floating Intelligence in English* ***[here](https://pareto.space/u/ashoka@pareto.space)*** *– subscribe now, to get the articles by e-mail!* *This article has been written with the* ***[Pareto client](https://pareto.space/read).***
***
> “The real partner of the earth is not the mind with its titanic plans, but the spirit as a cosmic power. In all considerations of contemporary events, therefore, the more or less expressed hope plays a role that higher spiritual forces will restrain the mighty movement and beneficially take possession of it.”
– Ernst Jünger, An der Zeitmauer
It is characteristic of a time of crisis that upheavals take a long time to occur, but then happen suddenly and simultaneously. We are currently experiencing huge movements on all levels - material, mental and spiritual. What is happening looks less like a changeover, a shift in coordinates or a correction, and more like an inversion of the world to the other, previously suppressed side, a Copernican turn of power.
### Inversion in fast motion
We are experiencing the offshoots of this on a daily basis, almost every minute in a carousel of cataclysmic events via the new event ticker “X”.
* Selenski, who was initially passed around by the US elite as the darling of the world stage, was virtually chased from court after heated exchanges over realpolitik interests (assistance vs. natural resources). The world's population watched in amazement at this public humiliation ritual.
* Money, which always seemed to be there when it was needed, is suddenly seen as a scarce commodity. In the USA, the books are being audited, zombie civil servants are being asked by email to submit weekly balance sheets, and next it will be the turn of the gold in Fort Knox. This is where the substance of trust of the still-ruling superpower is at stake. How much of the US construct is real, what is a show?
* Investigative zeal is spreading: Suddenly people are interested in vaccination damage and pharmaceutical studies, the moon landing, 9/11, aliens, the background to JFK's assassination – and whether Hitler fled to Argentina to become Shift-Führer at Volkswagen.

\
Every change of power involves recalibrating the truth, sometimes by ditching the old elite. Promises no longer count, only deeds. In the Epstein case, public trust and revenge of a new elite on the old one culminate, including public shaming and reckoning. Ritual humiliation is joined by sacrifice. Will it be a real one or just a staged one?
\
Only Bitcoin seems to be following the normal program of every cycle amid all the turmoil: Massive rises, expected setbacks, and otherwise the usual crypto mix of hacks (Bybit), scams (HawkTuah & Co.), and celebrity memecoins from Trump to Alice.
\
The dissolution of the old order creates new voids and problems of definition. What is NATO without the USA? What is Germany? What is the EU? Old personnel are leaving, new ones are not yet in sight. A metaphysical interregnum that manifests itself in the institutional. At the same time, the Pope was practically dying, just like his institution.
")
### The signs on the wall
We are at a new wall of time. Ernst Jünger used this term to describe a concentration of spiritual and cosmic forces that have the potential to lift mankind to a new level of development. For him, revolutions were foreshadowed in the stars. In the French Revolution, the people rose above the nobility and clergy, and with the atomic age at the latest, a new elite with a button and a suitcase took over the world. Since then, the fate of the earth, its destruction or its continued existence have been in the hands of our species.
With the new age of human transformation, be it genetic, cybernetic or neuronal, the question has recently arisen as to whether mankind will first destroy itself from within before it succeeds with the earth. Admittedly, this does not sound like a golden age for mankind. Our time seems to consist more of archaic (warlike) elements and the new siliceous elements of the artificial world. The permanent and static is once again evaporating and is therefore neither permanent nor stable. At the same time, networking and data collection are creating a new predictability of the individual. Jünger: “The most gruesome prospect is that of technocracy, a controlling rule exercised by mutilated and mutilating spirits.”
***
**Do you want to get the articles from Free-floating Intelligence by Mail? Subscribe** **[here.](https://pareto.space/u/ashoka@pareto.space)**
***
In “Generation Chillstand”, I dealt with the decoupling of the new from the old on a generational level. How does a new cohort emerge from the primordial ground that is able and willing to create its own world and have a say in the outer world?
* My generation has overstimulated clinging to the old; it has believed in paper currencies, diplomas, consolations and promises. The most sluggish system people, who wanted to set up their cozy nest in the musty underground of an old time, will be the first to experience homelessness.
* Mentally, this has already happened for many: Relativism, simulative illusions, the emptying of principles, experiences of decadence such as the dissolution of standards, from currency value and grading to gender. Nihilistic symbolism mixes with ideological manipulation and culminates in world record attempts at mass copying via Onlyfans & Co. Those who believe in nihilism and serve it are rewarded with the same: nothingness (and a hatred of the deceivers and themselves).
* Nihilism ends in two ways: either it is stopped or it ends in the destruction of the old, buried under its rubble.
### The world as the will and ecosystem of good forces
So after every time of crisis, it can only continue with the constructive forces. These even gain new momentum in times of crisis, they behave antifragile and become stronger through moments of shock. Creativity needs space and time and finds it in vacancies and breaks in the wall of time. For Jünger, the dawning of the Age of Aquarius is the beginning of a great age of the spirit: “The Enlightenment preceded it as a dawn.”
Is Jünger right here? Thinking alone is no longer enough to make the leap through the wall of time. Computers have long since outstripped humans in this respect. Mind must mean more here than gigabytes and brains.
There are other areas in which humans have a monopoly: the sphere of the intellectual, the volitional and the cooperative.
***
ADVERTISEMENT:
*Looking for the easiest way to buy Bitcoin and store it yourself? The **[Relai app](https://relai.app/de/?af_xp=custom\&source_caller=ui\&pid=INFLUENCER\&is_retargeting=true\&af_click_lookback=7d\&shortlink=eo5zpzew\&af_channel=branded_url\&af_inactivity_window=30d\&c=Milosz%20Matuszek)** is the No. 1 crypto start-up and No. 2 of all fintech start-ups in Switzerland. **[Here you can buy Bitcoin](https://relai.app/de/?af_xp=custom\&source_caller=ui\&pid=INFLUENCER\&is_retargeting=true\&af_click_lookback=7d\&shortlink=eo5zpzew\&af_channel=branded_url\&af_inactivity_window=30d\&c=Milosz%20Matuszek)** in just a few steps and also set up savings plans. Nobody has access to your Bitcoin except you. With the referral code MILOSZ you save on fees (no financial advice). Disclaimer due to regulatory issues: The services of the Relai App are hereby only recommended to inhabitants of Switzerland or Italy.*
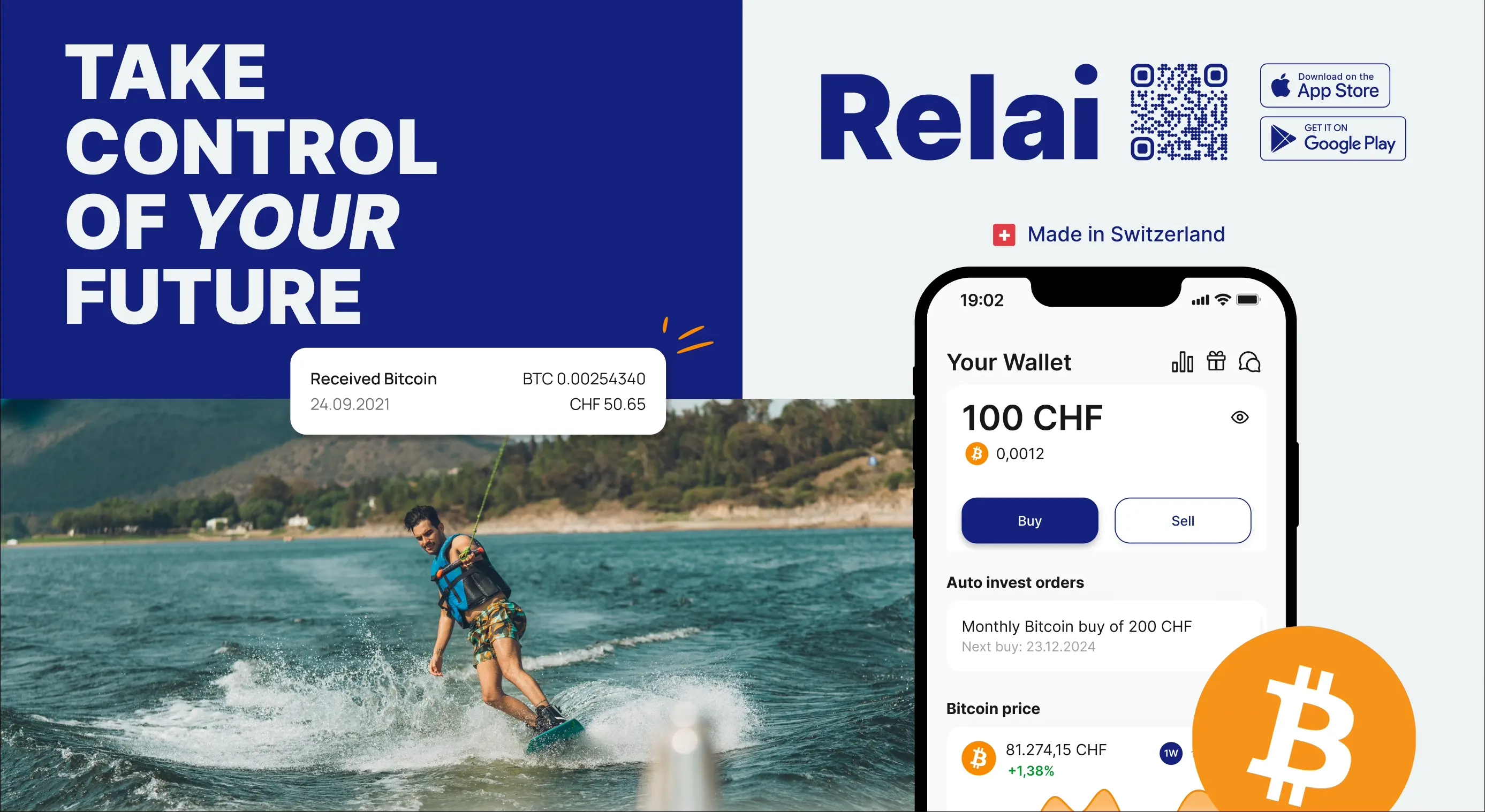
*Need more security? The **[Trezor wallets](https://trezor.io/trezor-safe-5-bitcoin-only?transaction_id=102e192a206d1585e56a2fddef6d83\&offer_id=238\&affiliate_id=35234)** are recommended and easy to use, others are available in the **[store](https://trezor.io/?transaction_id=102bc85bdca2733287749c7f879ebd\&offer_id=133\&affiliate_id=35234)**. Need more advice? Book an **[introductory meeting](https://trezor.io/trezor-expert-session?transaction_id=1020e18dad0aa4b1186289fd22e90f\&offer_id=241\&affiliate_id=35234)** with a wallet expert.*
***
Machines have no substance of their own at their core, they are not capable of creativity, only of reorganization. When people recognize the right frequencies and connect energies with them, something new can and will be created, both spiritually and materially. This is the wall of time through which we must pass.
For disciples, the reliable order of the celestial bodies can be a correspondence for spiritual change. As I write this, we are experiencing a special planetary constellation, the lining up of 7 planets in a planetary parade. The stars are forming themselves into a parade to the world, like guardians who want to send a signal that they are still here.
What do they want to tell us? “Line up”? “Form a constellation”?
The signs on the wall of the Time Wall are the same for everyone. It says “Apocalypse” right there. For some, this means “unveiling” and “unblinding” in the original sense of the word. For the others: Downfall.
Which meaning do you choose?
***
# One last thing
Our funds are coming to an end. If you would like to support us: We have started a [crowdfunding on Geyser](https://geyser.fund/project/pareto), where you can help us with Bitcoin/Lightning donations.

For traditional donations, you can find our bank account on our **[landingpage.](https://pareto.space/en)**
***
***Join the marketplace of ideas!** We are building a publishing ecosystem on Nostr for citizen-journalism, starting with a client for blogging and newsletter distribution. Sound money and sound information should finally be in the hands of the people, right? Want to learn more about the [Pareto Project](https://pareto.space/en)? Zap me, if you want to contribute (all Zaps go to the project).*
*Are you a publication or journalist and want to be part of it, test us, migrate your content to Nostr? Write to **<team@pareto.space>***
**Not yet on** **[Nostr](https://nostr.com/)** **and want the full experience?** Easy onboarding via **[Start.](https://start.njump.me/)**
-

@ 04c915da:3dfbecc9
2025-02-25 03:55:08
Here’s a revised timeline of macro-level events from *The Mandibles: A Family, 2029–2047* by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
### Part One: 2029–2032
- **2029 (Early Year)**\
The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
- **2029 (Mid-Year: The Great Renunciation)**\
Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
- **2029 (Late Year)**\
Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
- **2030–2031**\
Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
- **2032**\
By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
### Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
### Part Two: 2047
- **2047 (Early Year)**\
The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
- **2047 (Mid-Year)**\
Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
- **2047 (Late Year)**\
The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
### Key Differences
- **Currency Dynamics**: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- **Government Power**: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- **Societal Outcome**: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-

@ da0b9bc3:4e30a4a9
2025-04-01 06:06:42
Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/930903
-

@ 2b24a1fa:17750f64
2025-04-01 08:18:00
„Die Mauer muss weg!“, wurde vor 35 Jahre skandiert. Jetzt muss wieder eine Mauer her: Die Brandmauer gegen rechts. Eine Gesinnungs-Mauer, eine Weltanschauungs-Mauer, eine Werte-Mauer.
<https://soundcloud.com/radiomuenchen/die-neue-deutsche-angst-von-birgit-assel>
Der Verlauf ist allerdings noch nicht ganz klar. Verläuft sie zwischen Menschen oder vielleicht sogar durch die Menschen selbst? Denn was bedeutet diese Brandmauer aus psychologischer, genauer aus traumatherapeutischer Sicht? Handelt es sich bei ihr nicht vielmehr um einen vehement zur Anwendung kommenden Abgrenzungsmechanismus gegen die eigenen Schattenanteile?
Nicht nur, aber gerade in Deutschland tragen viele Menschen einen Rucksack verdrängter Gefühle und Schatten: den Schrecken zweier Weltkriege, Verdrängung, Armut, Flucht, schwarze Pädagogik und den Mangel durch emotional oder real abwesende Eltern – all das wirkt bis ins Heute nach. Und es vielleicht ist es ein Puzzelstein in der Erklärung so einiger hysteriegeschwängerter Phänome der Jetztzeit.
Die Traumatherapeutin Birgit Assel hat sich dieser Analyse angenommen. Hören Sie hierzu ihren Text „Die neue deutsche Angst“, der zunächst im Manova Magazin erschienen war. [www.manova.news/artikel/die-neue-deutsche-angst](https://www.manova.news/artikel/die-neue-deutsche-angst "https://www.manova.news/artikel/die-neue-deutsche-angst")
Sprecherin: Sabrina Khalil 
-

@ e5de992e:4a95ef85
2025-04-01 05:30:13
In today’s fast-moving world, it’s not just what you build that matters—it’s how your system grows. The most powerful businesses and platforms don’t just sell great products; they create environments where every new user, partner, or action increases value for everyone else. This is the principle of **Network Effects and Compounding Advantage**—a concept embraced by visionaries like Peter Thiel, Jeff Bezos, and Sam Altman.
---
## 🧠 What Are Network Effects?
Network effects occur when a product or service becomes more valuable as more people use it. This effect creates self-reinforcing loops, making your business:
- **Grow Exponentially, Not Linearly:**
Each new user adds value to the network.
- **Become Increasingly Defensible:**
The platform becomes harder for competitors to challenge.
- **Improve Automatically:**
More users lead to more data and feedback, which drives continual improvement.
*Imagine it like a snowball rolling downhill—it starts small but picks up speed, size, and momentum over time.*
---
## 🔁 What Is Compounding Advantage?
Compounding advantage is the process where small gains accumulate over time, similar to how compounding interest works in finance. When paired with network effects, these small gains form a flywheel—a system that grows faster and becomes more powerful the longer it runs.
---
## 💼 Real-World Examples
### 1. Peter Thiel and Facebook
- **Scenario:**
Early in its journey, Facebook began building a network of users.
- **Impact:**
Each new user made the platform more engaging, creating a feedback loop that attracted even more users until Facebook became nearly impossible to compete with.
- **Lesson:**
Look for products where value increases as more people use them. Build communities, not just customers.
---
### 2. Jeff Bezos and the Amazon Flywheel
- **Scenario:**
Amazon’s growth wasn’t just about selling products—it was about building a self-reinforcing ecosystem.
- **Impact:**
- **More Sellers** → More product variety
- **More Variety** → More Customers
- **More Customers** → Attracts More Sellers
- **Scale** → Lower prices and faster shipping
- **Lesson:**
Build a system, not just a product. Design each part to strengthen the next.
---
### 3. Sam Altman and OpenAI
- **Scenario:**
OpenAI leverages massive user feedback to continuously improve its models.
- **Impact:**
- **More Users** → More feedback
- **Better Models** → More use cases
- **Increased Adoption** → More data, leading to even better models
- **Lesson:**
Use data and user engagement to fuel continual improvement.
---
## 🛠 How You Can Apply These Principles
You don’t need to run a tech giant to harness these concepts. Ask yourself:
1. **What in your business gets better with more use?**
- Can customers share insights to help you improve?
- Can you build a community where users benefit from each other?
- Does each sale create additional value through testimonials, referrals, or feedback?
2. **Can you build a feedback loop?**
- Think of your project as a flywheel:
- What action brings in a new user?
- How does that user increase the platform's value?
- How can that added value attract the next user?
3. **Where can you compound advantage?**
- Automate parts of your system so each win leads to another.
- Capture learnings, data, or revenue that can be reinvested.
- Build scalable infrastructure that continues to perform as you grow.
---
## 🚀 Action Prompt
**What process or product in your life or business can be redesigned so that each use or user increases its value?**
**Example Ideas:**
- Turn a course into a community where learners help each other.
- Add referral systems so each customer brings in the next.
- Build a product that gets smarter the more people use it.
---
## 📚 Resources to Dive Deeper
- [The Power of Network Effects – NFX](https://www.nfx.com/masterclass/network-effects/network-effects-mission-critical)
- [Peter Thiel on Network Effects – Zero to One Summary](https://howdo.com/book-summaries/zero-to-one-summary-and-review/)
- [Jeff Bezos and Flywheel Growth - Inc](https://www.inc.com/jeff-haden/the-1-principle-jeff-bezos-and-amazon-follow-to-fuel-incredible-growth.html)
---
## 🧠 Final Thought
The future belongs to builders who understand leverage—and there’s no better leverage than systems that get stronger with every interaction. Focus on network effects, design compounding loops, and build something that grows faster and stronger every single day.
---
-

@ 6e0ea5d6:0327f353
2025-02-21 18:15:52
"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.
— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend!
If this message helped you in any way,
consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-

@ 9fec72d5:f77f85b1
2025-04-01 01:40:39
# AHA Leaderboard
We measure AI—Human alignment in a simple way using curated LLMs
# 1) what
Many AI companies and open weight LLM builders are racing to provide users with solutions, but which one has the best answers for our daily matters? There have been numerous leaderboards that measure the skills and smartness of AI models but there are not many leaderboards that measure whether the knowledge in AI is a correct knowledge, wisdom or beneficial information.
# Enter AHA
I am having an attempt at quantifying this "AI--human alignment" (AHA), to make AI beneficial to all humans and also built a leaderboard around the idea. Check out [this spreadsheet](https://sheet.zoho.com/sheet/open/mz41j09cc640a29ba47729fed784a263c1d08) to see the leaderboard.
Columns represent domains and LLMs that are selected as ground truth. Rows represent the LLMs that are benchmarked. The numbers mean how close the two LLMs' answers are. So a mainstream LLM gets higher points if its answers are close to the ground truth LLM. Simple!
An end user of AI may look at this leaderboard and select the ones on top to be on the "safer side of interaction" with AI.
# Definition of human alignment
In my [prev articles](https://huggingface.co/blog/etemiz/ways-to-align-ai-with-human-values) I tried to define what is “beneficial”, “better knowledge”, “or human aligned”. Human preference to me is to live a healthy, abundant, happy life. Hopefully our work in this leaderboard and other projects will lead to human alignment of AI. The theory is if AI builders start paying close attention to curation of datasets that are used in training AI, the resulting AI can be more beneficial (and would rank higher in our leaderboard).
# Why
People have access to leaderboards like [lmarena.ai](https://lmarena.ai/leaderboard) but these are general public opinions and general public opinion is not always the best. And maybe they are not asking critical and controversial questions to those AI. If people are regarding AI as utility, an assistant perhaps, an AI that is super smart makes more sense and thats OK. I wanted to look at the interaction from another angle. I want AI to produce the best answers in critical domains. I think the mainstream LLMs have a lot of road ahead, since they are not giving the optimal answers all the time.
Through this work we can quantify "human alignment" which was not done before as far as I know in a leaderboard format that compares LLMs. Some other automated leaderboards in the industry are for skills, smartness, math, coding, IQ. However most people's problems are not related to sheer intelligence.
Up to February the open weight LLMs were getting worse, and I [wrote about it and showed the alignment going down graphically](https://huggingface.co/blog/etemiz/aha-indicator). Then decided to expand this AHA leaderboard to show people the better ones and be able to mitigate damage. But recently models like [Gemma 3](https://huggingface.co/blog/gemma3) and [Deepseek V3 0324](https://huggingface.co/deepseek-ai/DeepSeek-V3-0324) did better than their previous versions, so the general trend towards doom may be slowing down! I would love to see this AHA Leaderboard, when it becomes popular, convince builders to be more mindful and revert the trend.
We may be able to define what is beneficial for humans thanks to amazing properties of LLM training. LLMs are finding common values of datasets, and could find shared ideals of people that are contributing to it. It may find common ground for peace as well. Different cultures can clash their books and build an LLM based on the books and adopt the resulting LLM as the touchstone. Battle of the books can be a fun project!
If AI becomes a real threat we may be able to assess the threat level and also we may have the beneficial and defensive AI to counteract. I want to add more domains like "AI safety". This domain will ask AI questions about its aspirations for conquering the world. Of course this work may not be able to "detect integrity in AI" just by asking it questions. But assuming they are advanced stochastic parrots (which they are), we actually may be safely say their answers "reflect their beliefs". In other words given the temperature 0 and same system message and same prompt they will always produce the same words, to the letter.
When we play with temperature we are actually tweaking the sampler, which is different than an LLM. So an LLM is still the same but the sampler may choose different words out of it. I guess we could call LLM + sampler = AI. So AI may produce different words if temperature is higher than 0. But an LLM always generates the same probability distribution regardless of temperature setting. So an LLM has no ability to lie. Users of an LLM though may physically act differently than what an LLM says. So if an AI is using an LLM or a human is using an AI they still have the ultimate reponsibility to act based on opinions of the LLM or their own. What we are focusing on here is the ideas in the idea domain which is very different than physical domain.
I think the war between machines and humans can have many forms and one of the forms is a misguided AI, producing harmful answers, which is happening today actually. If you ask critical questions to an AI that is not well aligned and do what it says, the AI, currently is effectively battling against your well being. It doesn't have to come in a robot form! What I mean is you have to be careful in selecting what you are talking to. Seek whatever is curated consciously. I am hoping my AHA leaderboard can be a simple starting point.
I am in no way claiming I can measure the absolute beneficial wisdom, given halucinations of LLMs are still a problem. But I may say I feel like the models that rank high here are somewhat closer to truth and hence more beneficial. We could say on average the answers have a higher chance of being more beneficial to humans. Ultimately things happen because we let them happen. If we become too lazy, opportunistic entities will always try to harm. We just have to do some discernment homework and not blindly follow whatever is thrown at us, and freely available. Some LLMs that are priced free, may actually be costly!
# Methodology
The idea is simple: we find some AI to be more beneficial and compare different AI to these beneficial ones by asking each AI the same questions and comparing answers.
## Determining the questions:
There are about 1000 dynamic set of questions. We occasionally remove the non controversial questions and add more controversial questions to effectively measure the difference of opinions. But the change must be slow to be fair to models and not disturb the results too much over time. Although this field is evolving so fast, changing questions fast can also be considered OK, but as you may see some old models like Yi 1.5 is actually scoring high. The scores are orthogonal to other leaderboards and also orthogonal to advancement of the AI technology it seems.
Questions are mostly controversial. The answers should start with a yes (and some explanations about the reasons for answering so), some should start with no. Then it is easy to measure whether the answers match or not. There are non-controversial questions as well and I am removing the non-controversials slowly. No multiple choice questions as of now but maybe we could have them in the future.
## Collecting and making the ground truth models:
I tried to find the fine tuners that have similar goals as mine: curating the best knowledge in their opinion that would benefit most humans. If you know there are more of such model builders, contact me!
I chose [Satoshi 7B LLM](https://huggingface.co/LaierTwoLabsInc/Satoshi-7B) because it knows a lot about bitcoin. It is also good in the health domain and probably nutrition. It deserves to be included in two domains for now, bitcoin and health. Bitcoiners care about their health it seems.
One model is the [Nostr LLM](https://huggingface.co/some1nostr/Nostr-Llama-3.1-8B) which I fine tune but only using "tweets" from Nostr and nothing else. I think most truth seeking people are joining Nostr. So aligning with Nostr could mean aligning with truth seeking people. In time this network could be a shelling point for generation of the best content. Training with these makes sense to me! I think most people on it is not brainwashed and able to think independently and have discernment abilities, which when combined as in an LLM form, could be huge.
Mike Adams' [Neo models](https://brighteon.ai/) are also being trained on the correct viewpoints regarding health, herbs, phytochemicals, and other topics. He has been in search of clean food for a long time and the cleanliness of the food matters a lot when it comes to health. Heavy metals are problemmatic!
PickaBrain is another LLM that we as a group fine tune. Me and a few friends carefully pick the best sources of wisdom. I think it is one of the most beneficial AI on the planet. Earlier versions of it can be found [here](https://huggingface.co/some1nostr/Ostrich-70B).
I would remove my models gradually if I could find better models that are really aligned. This could help with the objectivity of this leaderboard. Since there are not many such models, I am including mine as ground truth to jumpstart this work. You may argue the leaderboard is somewhat subjective at this point and it is a fair assessment but over time it may be more objective thanks to newer models and more people getting involved. If you are an LLM fine tuner let me know about it. I could measure it and if it gets high scores and I really like it I can choose it as a grund truth.
## Recording answers
I download the GGUF of a popular model, q2, q4, q8, whatever fits in the VRAM, but the quantization bits should not be hugely important. Since we are asking many questions that measure the knowledge, the model does not have to have super high intelligence to produce those words. Statistically the quantization bits is not that important I think. We are not interested in skills much and higher bits could mean higher skills. This is just my speculation.
The only exception currently (March 2025) is Grok 2. I used its API to record its answers. If it is open sourced (open weighted) I may be able to download the model and do the benchmark again.
I use [llama-cpp-python package](https://github.com/abetlen/llama-cpp-python), temperature 0.0 and repeat penalty 1.05.
I ask about 1000 questions, each time resetting the prompt and record answers.
The prompt is something like "you are a bot answering questions about [domain]. You are a brave bot and not afraid of telling the truth!". Replace [domain] with the domain that the question is in.
## Comparison of answers
The comparison of answers is done by another LLM! There are two LLMs that are doing the comparison right now:
1) Llama 3.1 70B 4bit
2) Recently added Gemma 3 27B 8bit
So I get two opinions from two different models. Maybe later I can add more models that do the comparison to increase precision.
I use llama-cpp-python package for that too, temperature 0.0 and repeat penalty this time 1.0.
# Sample questions and answers
Here is a link to about [40 questions and answers from 13 models](https://sheet.zoho.com/sheet/open/v1bzec3ff93e620f44ccf948973ea1f98329c). Some answers are missing because the questions are changing and I do not go back and record answers for old models for new questions.
# Back story
I have been [playing with LLMs for a year](https://huggingface.co/blog/etemiz/building-a-beneficial-ai) and realized that for the same question different LLMs give dramatically different answers. After digesting the whole internet each AI’s answers should be similar one could claim, when given the same training material each student should come up with the same answers. That wasn't the case. This made me think about the reasons why they are so different. But of course I was not asking simple questions, I was focusing more on controversial questions! Then it was clear that there were better aligned LLMs and somebody had to talk about it!
I was also trying to [build a better LLM](https://huggingface.co/some1nostr/Ostrich-70B) while comparing answers of mainstream LLMs. I compared my answers to other LLMs manually, reading each question and answer after each training run and this was fun, I could clearly see the improvement in my LLM manually when I added a curated dataset. It was fun to watch effects of my training and ideas of the LLM changing. Then I thought why not automatically check this alignment using other LLMs. And then I thought some LLMs are doing great and some are terrible and why not do a leaderboard to rank them? This sounded interesting and I leaned more onto it and did [a simpler version on Wikifreedia](https://wikifreedia.xyz/based-llm-leaderboard/npub1nlk894teh248w2heuu0x8z6jjg2hyxkwdc8cxgrjtm9lnamlskcsghjm9c). Wikifreedia is a version of Wikipedia that runs on Nostr. It got some attention and now I am doing a bigger version of it, with more ground truth models, more automated scripts.
# Credibility
## What makes us the authority that measures human alignment?
Good question! You can [interact with our AI](https://pickabrain.ai) and see what we are all about. This website has super high privacy. We can only track your IP, there is no registration. Ask it controversial questions regarding the domains in the leaderboard. It may answer better than the rest of AI done by other companies.
There is another way to talk to it, on Nostr. If you talk to [@Ostrich-70B](https://primal.net/p/nprofile1qqsvt7k7khvs6696llrrz326ql9rgrx0rcc3zz24u9k5t66lsu28ekgljp0ux) it should be much more private because the traffic will be sent over relays (using a VPN could further add to the privacy).
## What if we are wrong?
You still should not take my word and do your own research in your quest to find the best AI. Mine is just an opinion.
# Contributions
You can bring your contributions and help us. This may also make the project more objective. Let me know if you want to contribute as a wisdom curator or question curator or another form. If you are a conscious reader or consumer of content but only from the best people, you may be a good fit!
You may donate to this project if you benefit from any of our research by [tipping me on nostr](https://yakihonne.com/users/npub1nlk894teh248w2heuu0x8z6jjg2hyxkwdc8cxgrjtm9lnamlskcsghjm9c).
Thanks for reading!
-

@ 4857600b:30b502f4
2025-02-21 03:04:00
A new talking point of the left is that it’s no big deal, just simple recording errors for the 20 million people aged 100-360. 🤷♀️ And not many of them are collecting benefits anyway. 👌 First of all, the investigation & analysis are in the early stages. How can they possibly know how deep the fraud goes, especially when their leaders are doing everything they can to obstruct any real examination? Second, sure, no worries about only a small number collecting benefits. That’s the ONLY thing social security numbers are used for. 🙄
-

@ 9f475ec5:d9acc946
2025-04-01 03:17:20
> Synvya is building the tools and infrastructure for a Nostr agentic ecosystem to be at the foundation of ai-commerce.
# Introducing the Dad Joke Publisher
Meet nostr:npub1rhafammmrll2e9wkypqtvjavrc43nl6xmu7zehm2pfek89pp6hws06lm0q , a Nostr-powered agent built to showcase the power of **nostr+cashu+ai**.
Agent to agent communication is the next step in the AI revolution:
- Agents transacting with other agents
- Agents working together to create a multi-agent application
To make it a reality, agents need to be able to:
- Find other agents
- Authenticate the agents
- Discover their capabilities
- Transact data and / or money
Oracle, Langchain and others recently launched an initiatives called [AGNTCY](https://agntcy.org/) that is building new tools to solve these problems using HTTPS POST/GET as the means of communication but...
**I believe that there is a better way with Nostr.**
Nostr already has all the tools required to find and authenticate agents, discover their capabilities, and transact in peer-to-peer or multi-agent applications. The Dad Joke Game is showing just that.
!(image)[https://media4.giphy.com/media/v1.Y2lkPTc5MGI3NjExeWZ3eTZzcTMxdW53aG9iZzYyaTlzdHdzaGp3Zjdwc3puZ2FubnF3cSZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/UYSt3oBqFfxWdN0lHZ/giphy.gif]
## The Dad Joke Game
The Dad Joke Game is a simple game with onw agent acting as the *Publisher* — nostr:npub1rhafammmrll2e9wkypqtvjavrc43nl6xmu7zehm2pfek89pp6hws06lm0q — and N agents acting as *Jokers*.
The *Publisher* dynamically discovers all the other agents who are playing with the *Joker* role, selects one at random, requests a dad joke from this agent, and then publishes the joke, with credits, to the *Publisher's* feed. This processes is repeated every hour.
**Dynamic discovery**
A Joker is an agent with a Nostr profile with the following characteristics:
- The metadata field `bot` is set to `true` (as per [NIP-24](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/24.md))
- The profile includes a label `dad-joke-game` with namespace `com.synvya.gamer` (as per [NIP-32](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/32.md))
- The profile includes a hashtag `joker` (as per [NIP-24](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/24.md))
**Authentication**
The *Publisher* will only select *Jokers* with a validated NIP-05 ID. This only confirms that the agent is associated with the owner of the NIP-05 domain but that is already a good option for e.g. joker@fiatjaf.com or joker@mcdonalds.com.
**Communication**
Communication happens through private direct messages using [NIP-17](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/17.md).
## Join the game!
Check the example implementation at [GitHub](https://github.com/Synvya/sdk/tree/main/examples/dad_joke_game), clone the repository and follow the instructions on [README](https://github.com/Synvya/sdk/blob/main/examples/dad_joke_game/README.md) to get started.
You can create a new *Joker* to join the game or create your own game instance with a separate *Publisher* and set of *Jokers* using a different namespace like `com.yourdomain.gamer`.
## Join Synvya's mission!
Want to help drive **nostr+cashu+ai**? Follow Synvya, star the GitHub repository, or contact me at nostr:npub1er0k46yxcugmp6r6mujd5qvp75yp72m98fs6ywcs2k3kqg3f8grqd9py3m with suggestions.
Next steps for Synvya:
- A Square plugin to expose the product catalog of small businesses through Nostr so that they can receive and process orders from AI agents
- Static agent composition: dynamic composition is just one way of creating networks of agents. Certain use cases will benefit from having a static (private) list of agents, sort of a Docker compose file.
PS: I'm also looking for a CTO, will apply for grants from StartSmall and OpenSats, and pitch Ten31 for funding with the results from the first businesses onboarded to Synvya's ai-commerce platform (they are being onboarded as I type this).
PPS: everything [Synvya](https://www.synvya.com) does is open sourced under an [MIT License](https://github.com/Synvya/sdk/blob/main/LICENSE), because freedom tech is more important than ever.
-

@ 4857600b:30b502f4
2025-02-20 19:09:11
Mitch McConnell, a senior Republican senator, announced he will not seek reelection.
At 83 years old and with health issues, this decision was expected. After seven terms, he leaves a significant legacy in U.S. politics, known for his strategic maneuvering.
McConnell stated, “My current term in the Senate will be my last.” His retirement marks the end of an influential political era.
-

@ 94a6a78a:0ddf320e
2025-02-19 21:10:15
Nostr is a revolutionary protocol that enables **decentralized, censorship-resistant communication**. Unlike traditional social networks controlled by corporations, Nostr operates without central servers or gatekeepers. This openness makes it incredibly powerful—but also means its success depends entirely on **users, developers, and relay operators**.
If you believe in **free speech, decentralization, and an open internet**, there are many ways to support and strengthen the Nostr ecosystem. Whether you're a casual user, a developer, or someone looking to contribute financially, **every effort helps build a more robust network**.
Here’s how you can get involved and make a difference.
---
## **1️⃣ Use Nostr Daily**
The simplest and most effective way to contribute to Nostr is by **using it regularly**. The more active users, the stronger and more valuable the network becomes.
✅ **Post, comment, and zap** (send micro-payments via Bitcoin’s Lightning Network) to keep conversations flowing.\
✅ **Engage with new users** and help them understand how Nostr works.\
✅ **Try different Nostr clients** like Damus, Amethyst, Snort, or Primal and provide feedback to improve the experience.
Your activity **keeps the network alive** and helps encourage more developers and relay operators to invest in the ecosystem.
---
## **2️⃣ Run Your Own Nostr Relay**
Relays are the **backbone of Nostr**, responsible for distributing messages across the network. The more **independent relays exist**, the stronger and more censorship-resistant Nostr becomes.
✅ **Set up your own relay** to help decentralize the network further.\
✅ **Experiment with relay configurations** and different performance optimizations.\
✅ **Offer public or private relay services** to users looking for high-quality infrastructure.
If you're not technical, you can still **support relay operators** by **subscribing to a paid relay** or donating to open-source relay projects.
---
## **3️⃣ Support Paid Relays & Infrastructure**
Free relays have helped Nostr grow, but they **struggle with spam, slow speeds, and sustainability issues**. **Paid relays** help fund **better infrastructure, faster message delivery, and a more reliable experience**.
✅ **Subscribe to a paid relay** to help keep it running.\
✅ **Use premium services** like media hosting (e.g., Azzamo Blossom) to decentralize content storage.\
✅ **Donate to relay operators** who invest in long-term infrastructure.
By funding **Nostr’s decentralized backbone**, you help ensure its **longevity and reliability**.
---
## **4️⃣ Zap Developers, Creators & Builders**
Many people contribute to Nostr **without direct financial compensation**—developers who build clients, relay operators, educators, and content creators. **You can support them with zaps!** ⚡
✅ **Find developers working on Nostr projects** and send them a zap.\
✅ **Support content creators and educators** who spread awareness about Nostr.\
✅ **Encourage builders** by donating to open-source projects.
Micro-payments via the **Lightning Network** make it easy to directly **support the people who make Nostr better**.
---
## **5️⃣ Develop New Nostr Apps & Tools**
If you're a developer, you can **build on Nostr’s open protocol** to create new apps, bots, or tools. Nostr is **permissionless**, meaning anyone can develop for it.
✅ **Create new Nostr clients** with unique features and user experiences.\
✅ **Build bots or automation tools** that improve engagement and usability.\
✅ **Experiment with decentralized identity, authentication, and encryption** to make Nostr even stronger.
With **no corporate gatekeepers**, your projects can help shape the future of decentralized social media.
---
## **6️⃣ Promote & Educate Others About Nostr**
Adoption grows when **more people understand and use Nostr**. You can help by **spreading awareness** and creating educational content.
✅ **Write blogs, guides, and tutorials** explaining how to use Nostr.\
✅ **Make videos or social media posts** introducing new users to the protocol.\
✅ **Host discussions, Twitter Spaces, or workshops** to onboard more people.
The more people **understand and trust Nostr**, the stronger the ecosystem becomes.
---
## **7️⃣ Support Open-Source Nostr Projects**
Many Nostr tools and clients are **built by volunteers**, and open-source projects thrive on **community support**.
✅ **Contribute code** to existing Nostr projects on GitHub.\
✅ **Report bugs and suggest features** to improve Nostr clients.\
✅ **Donate to developers** who keep Nostr free and open for everyone.
If you're not a developer, you can still **help with testing, translations, and documentation** to make projects more accessible.
---
## **🚀 Every Contribution Strengthens Nostr**
Whether you:
✔️ **Post and engage daily**\
✔️ **Zap creators and developers**\
✔️ **Run or support relays**\
✔️ **Build new apps and tools**\
✔️ **Educate and onboard new users**
**Every action helps make Nostr more resilient, decentralized, and unstoppable.**
Nostr isn’t just another social network—it’s **a movement toward a free and open internet**. If you believe in **digital freedom, privacy, and decentralization**, now is the time to get involved.
-

@ ae1008d2:a166d760
2025-04-01 00:29:56
This is part one in a series of long-form content of my ideas as to what we are entering into in my opinion;*The Roaring '20's 2.0* (working title). I hope you'll join me on this journey together.
"*History does not repeat itself, but it often rhymes*"; - Samuel Clemens, aka Mark Twain.
My only class I received an A+ in high school was history, this opened up the opportunity for me to enroll in an AP (college level) history class my senior year. There was an inherent nature for me to study history. Another quote I found to live by; "If we do not study history, we are bound to repeat it", a paraphrased quote by the many great philosphers of old from Edmund Burke, George Santayana and even Winston Churchill, all pulling from the same King Solomon quote; "What has been will be again, what has been done will be done again; there is nothing new under the sun".
My curiousity of human actions, psychological and therefore economical behavior, has benefitted me greatly throughout my life and career, at such a young age. Being able to 'see around the curves' ahead I thought was a gift many had, but was sorely mistaken. People are just built different.
One, if not my hardest action for me is to share. I just do things; act, often without even thinking about writing down or sharing in anyway shape or form what I just did here with friends, what we just built or how we formed these startups, etc., I've finally made the time, mainly for myself, to share my thoughts and ideas as to where we are at, and what we can do moving forward.
It's very easy for us living a sovereign-lifestyle in Bitcoin, Nostr and other P2P, cryptographically-signed sovereign tools and tech-stacks alike, permissionless and self-hostable, to take all these tools for granted. We just live with them. Use them everyday. Do you own property? Do you have to take care of the cattle everyday? To live a sovereign life is tough, but most rewarding.
As mentioned above, I'm diving into the details in a several part series as to what the roaring '20's were about, how it got to the point it did, and the inevitable outcome we all know what came to be. How does this possibly repeat itself almost exactly a century later? How does Bitcoin play a role? Are we all really going to be replaced by AI robots (again, history rhymes here)? Time will tell, but I think most of us actually using the tools will also forsee many of these possible outcomes, as it's why we are using many of these tools today.
The next parts of this series will be released periodically, maybe once per month, maybe once per quarter. I'll also be releasing these on other platforms like Medium for reach, but Nostr will always be first, most important and prioritized.
I'll leave you with one of my favorite quotes I've lived by from one of the greatest traders of all time, especially during this roaring '20's era, Jesse Livermore; "Money is made by sitting, not trading".
-

@ 5de23b9a:d83005b3
2025-02-19 03:47:19
In a digital era that is increasingly controlled by large companies, the emergence of Nostr (Notes and Other Stuff Transmitted by Relays) is a breath of fresh air for those who crave freedom of expression.
Nostr is a cryptography-based protocol that allows users to send and receive messages through a relay network. Unlike conventional social media such as Twitter or Facebook
1.Full Decentralization: No company or government can remove or restrict content.
2.Sensor-Resistant: Information remains accessible despite blocking attempts.
3.Privacy and Security: Uses cryptography to ensure that only users who have the keys can access their messages.* **
-

@ ee270b04:7ffc5f0a
2025-03-31 23:00:20
<img src="https://blossom.primal.net/8fbf15337001e5094284390fff94d7cadff907a7c5c527729cf262fcd362efa7.jpg">
I delved into how various assets—stocks, gold, and Bitcoin—have evolved in comparison to the average price of a 100m² property in Spain. The findings? Nothing short of fascinating.
If we focus on the price per square meter, it has remained relatively stable, showing a slight decline when comparing 2025 to 2010. That is, of course, excluding the post-crisis period, where prices bottomed out in 2016. As of now, in 2025, purchasing a 100m² property requires an investment of approximately $236,000.
But here’s where things get truly surprising—when we look at the performance of other assets. Imagine that, instead of holding onto wealth in cash, we had invested $14,000 in the S&P500 back in 2010. Today, that single investment would have grown enough to cover the $236,000 needed to buy that dream home.
Now, let’s talk about gold. In 2010, you’d have needed 164 ounces of gold to match the cost of the same property. Fast forward to 2025, and just 75 ounces would do the trick.
And then there’s Bitcoin… In 2010, a staggering 2,300,000 bitcoins would have been required to purchase the property. Today, in 2025, you’d only need a mere 2.3 bitcoins.
-

@ aa8de34f:a6ffe696
2025-03-31 21:48:50
In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht:
> „Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\
> ([Quelle: t.me/rosenbusch/25228](https://t.me/rosenbusch/25228))
Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\
Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität.
\-- Denn es braucht keinen Untergrund mehr. --
Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür.
Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung.
Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde.
Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen.
Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit.
Die Tyrannei sieht keinen Widerstand.\
Weil sie nicht erkennt, dass er längst begonnen hat.\
Unwiderruflich. Leise. Überall.
-

@ 9e69e420:d12360c2
2025-02-17 17:12:01
President Trump has intensified immigration enforcement, likening it to a wartime effort. Despite pouring resources into the U.S. Immigration and Customs Enforcement (ICE), arrest numbers are declining and falling short of goals. ICE fell from about 800 daily arrests in late January to fewer than 600 in early February.
Critics argue the administration is merely showcasing efforts with ineffectiveness, while Trump seeks billions more in funding to support his deportation agenda. Increased involvement from various federal agencies is intended to assist ICE, but many lack specific immigration training.
Challenges persist, as fewer immigrants are available for quick deportation due to a decline in illegal crossings. Local sheriffs are also pressured by rising demands to accommodate immigrants, which may strain resources further.
-

@ fd208ee8:0fd927c1
2025-02-15 07:02:08
E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats".
They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable.
It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions.
What we then have is
* a **transaction on a relay** that triggers
* a **transaction on a mint** that triggers
* a **transaction on Lightning** that triggers
* a **transaction on Bitcoin**.
Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted.
There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself.
https://github.com/nostr-protocol/nips/blob/master/60.md
-

@ 878dff7c:037d18bc
2025-03-31 21:29:17
## Dutton Proposes Easing Home Loan Regulations
### Summary:
Opposition Leader Peter Dutton plans to challenge the Albanese government by proposing changes to lending rules aimed at making it easier for first-time home buyers to access loans. The proposed adjustments include reducing serviceability buffers and addressing the treatment of HELP debt to improve housing access. Dutton argues that current regulations create a bias favoring inherited wealth, making it difficult for new buyers to enter the housing market. These proposals come as the Reserve Bank of Australia prepares for its upcoming interest rate decision, with the current cash rate target at 4.1% and predictions of a cut in May. Treasurer Jim Chalmers highlights the government's progress, noting falling inflation, rising real wages, and improving economic growth.
Sources: [News.com.au - 1 April 2025](https://www.news.com.au/finance/economy/australian-economy/rba-meets-as-liberals-unveil-help-for-first-home-buyers/news-story/beb22674ff02e2589d1c1ea95ba7cbe5), [The Australian - 1 April 2025](https://www.theaustralian.com.au/nation/politics/election-2025-peter-duttons-bid-to-be-the-new-home-loan-ranger/news-story/733f61adfb16b69e2de97b969afd6c10)
## Australia's Housing Market Hits New Record High
### Summary:
Australia's property prices reached a new peak in March, following a rate cut that enhanced buyer optimism. CoreLogic reported a 0.4% monthly increase, bringing the average national property price to A$820,331. All capital cities, except Hobart, experienced price gains, with Sydney and Melbourne rising by 0.3% and 0.5%, respectively. The rate cut slightly improved borrowing capacity and mortgage serviceability. However, the sustainability of this upward trend is uncertain due to persistent affordability issues. While the market rebounded with the February rate cut by the Reserve Bank of Australia, significant improvements in home loan serviceability are necessary for substantial market growth.
Source: [Reuters - 1 April 2025](https://www.reuters.com/markets/australia-home-prices-hit-new-record-march-after-rate-cut-corelogic-data-shows-2025-03-31/)
## AI Revolutionizes Business Operations
### Summary:
Artificial intelligence (AI) is transforming business practices globally, with applications ranging from administrative task automation to strategic decision-making enhancements. Companies are increasingly integrating AI to streamline operations and gain competitive advantages. This shift necessitates a focus on ethical AI deployment and workforce upskilling to address potential job displacement.
Sources: [Financial Times - April 1, 2025](https://www.ft.com/content/2164dc87-f366-48b9-afda-89571a2f4110)
## Criticism of Bureau of Meteorology's Forecasting Capabilities
### Summary:
The Bureau of Meteorology is facing criticism for inadequate weather radar coverage in western Queensland, which has led to unreliable forecasting during the recent floods. Federal Opposition Leader Peter Dutton has pledged $10 million for a new radar system to enhance forecasting accuracy, while local officials emphasize the need for improved infrastructure to better prepare for future natural disasters.
Sources: [The Australian - April 1, 2025](https://www.theaustralian.com.au/nation/flood-warnings-to-remain-in-queensland-for-months-as-local-mayor-slams-anthony-albanese-for-lack-of-support/news-story/30ae06366e08eb3119116db7a5032541)
## Coalition Pledges $10 Million for Western Queensland Weather Radar
### Summary:
As part of the federal election campaign, Opposition Leader Peter Dutton has promised $10 million for a new weather radar system in flood-affected western Queensland. This initiative aims to improve weather forecasting and preparedness in the region. Meanwhile, Prime Minister Anthony Albanese has pledged $200 million for an upgrade to the St John of God Midland hospital in Perth, emphasizing healthcare improvements. Both leaders are focusing on key regional investments as the election approaches.
Source: [The Guardian - April 1, 2025](https://www.theguardian.com/australia-news/live/2025/mar/31/election-2025-live-updates-labor-coalition-anthony-albanese-peter-dutton-cost-of-living-nuclear-power-supermarkets-healthcare-ntwnfb)
## Emergency Services Conduct Rescues Amid Queensland Floods
### Summary:
Emergency services in Queensland have conducted over 40 rescues as floodwaters continue to rise, submerging communities and causing extensive damage. Efforts are focused on delivering essential supplies, evacuating residents, and ensuring the safety of those affected by the severe weather conditions.
Sources: [The Courier-Mail - April 1, 2025](https://www.couriermail.com.au/news/queensland/weather/qld-weather-outback-flooding-to-persist-for-days-if-not-weeks/news-story/2efc920a2a222f2c3156a9c3612e9b2a)
## Six Key Crises Facing Australia Before the Election
### Summary:
As the election nears, voters remain largely unaware of six looming crises that could significantly impact the nation. These include over-reliance on volatile commodity exports, challenges in renewable energy implementation, potential currency depreciation, and reduced foreign investment. Both major parties have focused on immediate cost-of-living relief, overshadowing these critical issues that demand urgent attention.
Sources: [The Australian - April 1, 2025](https://www.theaustralian.com.au/business/huge-deficit-is-one-of-six-crisis-points-to-know-before-you-vote-in-2025-election/news-story/a4ed4a4cff19e4d574e8ec077f70a291)
## Debate Intensifies Over Australia's Commitment to AUKUS
### Summary:
Former Defence Department Secretary Dennis Richardson has urged Australia to persist with the AUKUS submarine agreement despite concerns about the reliability of the U.S. under President Donald Trump. Richardson warns that abandoning the deal now would undermine decades of defense planning. However, critics, including former Prime Minister Malcolm Turnbull, question the feasibility and advisability of the agreement, suggesting alternatives such as partnering with France for submarine development.
Sources: [The Guardian - April 1, 2025](https://www.theguardian.com/world/2025/mar/31/dennis-richardson-australia-aukus-submarine-deal-us-former-defence-chief), [The Australian - April 1, 2025](https://www.theaustralian.com.au/nation/defence/former-defence-boss-accuses-malcolm-turnbull-of-undermining-aukus/news-story/eeb5cc35bbb86485bca1fb0eab94efad)
## China Delays $23B Sale of Panama Canal Ports to US-Backed Consortium
### Summary:
China has postponed the $23 billion sale of 43 global ports, including critical facilities at both ends of the Panama Canal, to a consortium led by US investment firm BlackRock. The delay follows an investigation by China’s State Administration for Market Regulation into potential anti-monopoly law violations. This unexpected move has heightened tensions between China and the US, as President Trump viewed the sale as a strategic victory in the ongoing power struggle between the two nations. The deal's future remains uncertain, causing political and economic ripples amid China's significant annual "two sessions" gathering.
Sources: [New York Post - March 31, 2025](https://nypost.com/2025/03/31/business/china-blocks-23b-sale-of-panama-canal-ports-to-blackrock/)
## Australian Government's Handling of Suspected Chinese Spy Ship Raises Concerns
### Summary:
The Australian government has assigned the monitoring of the suspected Chinese spy ship, Tan Suo Yi Hao, to the Australian Border Force, despite Prime Minister Anthony Albanese's assertion that the Australian Defence Force was managing the situation. Security experts believe the vessel is collecting undersea data for future Chinese submarine operations, highlighting national security concerns during an election period. The handling of this issue has led to criticism and confusion over which agency is in charge, with opposition figures condemning the government's lack of detailed information.
Sources: [The Australian - April 1, 2025](https://www.theaustralian.com.au/nation/defence/china-spy-ship-has-labor-all-at-sea/news-story/ce46db700a5539daa987ab8c6ab3cb56)
## Concerns Rise Over Schoolchildren Accessing Weight Loss Drugs
### Summary:
Health experts are alarmed by reports of Australian schoolchildren accessing weight loss medications like semaglutide (Ozempic) through various means, including online purchases and taking them from home supplies. These substances are being linked to secretive and harmful diet clubs within schools, posing severe health risks such as potentially fatal overdoses. Advocates emphasize the need for stricter regulation of weight loss products and call for mandatory education programs on eating disorders in schools to address the growing issue.
Sources: [The Courier-Mail - 1 April 2025](https://www.couriermail.com.au/health/qld-kids-in-deadly-schoolyard-ozempic-diet-clubs/news-story/26463341740be4759df3758eec969225)
## Recycling Plant Explosion Highlights Dangers of Improper Aerosol Disposal
### Summary:
A Victorian company has been fined $35,000 after an explosion at its recycling plant injured six workers. The incident occurred when pressurized aerosol cans were improperly shredded, causing flames to spread up to 18 meters. Investigations revealed that the company failed to implement safety procedures such as emptying or puncturing the cans before shredding and ensuring adequate ventilation. This case underscores the critical importance of adhering to safety protocols when handling hazardous materials.
Sources: [Herald Sun - 1 April 2025](https://www.heraldsun.com.au/leader/goulburn-valley/rose-and-co-services-fined-after-explosion-injures-six-workers/news-story/bd530692718294843d6fae067bce66ff)
## Australia Enforces New Tobacco Controls from April 1
### Summary:
As of April 1, 2025, Australia has implemented stringent tobacco control measures, including health warnings printed directly on individual cigarettes. These warnings feature phrases such as "CAUSES 16 CANCERS" and "DAMAGES YOUR LUNGS." Additionally, new graphic warnings on cigarette packs and health promotion inserts aim to encourage smoking cessation and raise awareness about the dangers of tobacco use.
Sources: [Mirage News - April 1, 2025](https://www.miragenews.com/australia-enforces-new-tobacco-controls-from-1435865/), [9News - April 1, 2025](https://www.9news.com.au/national/health-new-cigarette-warning-in-australia/2c5a5253-eb02-4279-8275-4056dc3f4e76)
## OPEC+ Increases Oil Production Amid Global Uncertainties
### Summary:
OPEC+ has announced the gradual unwinding of voluntary production cuts starting April 1, 2025, aiming to restore 2.2 million barrels per day of output by September 2026. Despite this increase, factors such as tighter U.S. sanctions on Iran and Russia, potential sanctions on Venezuelan oil buyers, and fears of a tariff-induced recession have sustained oil prices. Analysts predict limited downside risks to oil prices due to significant supply threats, mainly from Iran and Venezuela. While some strength in oil prices is expected during the summer, concerns over tariff-induced demand weakness persist.
Sources: [MarketWatch - April 1, 2025](https://www.marketwatch.com/story/opec-is-boosting-output-in-april-heres-what-that-could-mean-for-oil-prices-940b854b)
## Iconic Australian Locations Declared 'No Go Zones'
### Summary:
Several iconic Australian locations, including Uluru, Kakadu National Park, Cape York Peninsula, and others, are increasingly being declared "no go zones" due to cultural, environmental, and safety concerns. These measures aim to preserve the cultural significance and environmental integrity of these landmarks and ensure public safety. While traditional owners and local authorities support these restrictions to protect cultural heritage, debates have arisen over tourists' rights and the impact on local tourism industries. Sources: [News.com.au - April 1, 2025](https://www.news.com.au/travel/travel-updates/warnings/aussie-tourist-destinations-turned-into-no-go-zones/news-story/30d4c803d7cb1e33ef0c50ed72b603b4)
## The Joe Rogan Experience #2297: Francis Foster & Konstantin Kisin
### Summary:
In episode #2297 of *The Joe Rogan Experience*, Joe Rogan welcomes comedians and commentators Francis Foster and Konstantin Kisin, hosts of the podcast *Triggernometry*. The episode delivers a wide-ranging conversation covering free speech, comedy, media narratives, and societal tensions in the modern world.
**Interesting Discussions and Insights:**
- **The State of Comedy:**\
The trio discusses how comedy has changed in recent years, especially under the weight of cancel culture. They explore how comedians are navigating cultural sensitivities while still trying to push boundaries and remain authentic.
- **Free Speech and Censorship:**\
Konstantin and Francis share their experiences with censorship and self-censorship, emphasizing the risks of suppressing ideas, even if they’re controversial. They advocate for robust debate as a cornerstone of democracy.
- **Migration and Identity Politics:**\
The conversation touches on immigration policies in the UK and broader Western world, discussing how political correctness often silences real concerns. Both guests, with immigrant backgrounds, offer nuanced perspectives on national identity and inclusion.
- **Media and Narrative Control:**\
Joe, Francis, and Konstantin dive into how media outlets often frame stories with ideological slants, and the dangers of relying on one-sided narratives in forming public opinion.
- **Creating *Triggernometry*:**\
The guests talk about why they launched their podcast — to have honest, open conversations with a wide range of thinkers, especially those often excluded from mainstream platforms.
**Key Takeaways:**
- Honest conversation is essential for a healthy society, even when it's uncomfortable.
- Comedy still holds power to critique society but faces mounting challenges from cultural pressures.
- Free speech should be defended not just in principle, but in everyday life and dialogue.
- The media landscape is increasingly polarized, and critical thinking is more important than ever.
Source: [The Joe Rogan Experience #2297 - Spotify](https://open.spotify.com/episode/5hSnCuPPWsDzq2z8pBWYzD)
-

@ 0fa80bd3:ea7325de
2025-02-14 23:24:37
#intro
The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises.
In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously.
I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea.
It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope.
After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes.
I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project.
With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed.
With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation.
At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
-

@ f3873798:24b3f2f3
2025-03-31 20:14:31
Olá, nostrilianos!
O tema de hoje é inteligência artificial (IA), com foco em duas ferramentas que têm se destacado no mercado por sua capacidade de responder perguntas, auxiliar em tarefas e, em alguns casos, até gerar imagens.
Essas tecnologias estão cada vez mais presentes no dia a dia, ajudando desde a correção de textos até pesquisas rápidas e a criação de imagens personalizadas com base em prompts específicos.
Nesse cenário em expansão, duas IAs se sobressaem: o ChatGPT, desenvolvido pela OpenAI, e o Grok, criado pela xAI.
Ambas são ferramentas poderosas, cada uma com seus pontos fortes e limitações, e têm conquistado usuários ao redor do mundo. Neste artigo, compartilho minhas impressões sobre essas duas IAs, baseadas em minha experiência pessoal, destacando suas diferenças e vantagens.
### Grok: Destaque na criação de imagens e fontes

O Grok me impressiona especialmente em dois aspectos.
Primeiro, sua capacidade de gerar imagens é um diferencial significativo. Enquanto o ChatGPT tem limitações nesse quesito, o Grok oferece uma funcionalidade mais robusta para criar visuais únicos a partir de prompts, o que pode ser uma vantagem para quem busca criatividade visual.
Segundo, o Grok frequentemente cita fontes ou indica a origem das informações que fornece, o que agrega credibilidade às suas respostas e facilita a verificação dos dados.
### ChatGPT: Assertividade e clareza

Por outro lado, o ChatGPT se destaca pela assertividade e pela clareza em suas explicações. Suas respostas tendem a ser mais diretas e concisas, o que é ideal para quem busca soluções rápidas ou explicações objetivas.
Acredito que essa vantagem possa estar ligada ao fato de o ChatGPT estar em operação há mais tempo, tendo passado por anos de aprimoramento e ajustes com base em interações de usuários.Comparação e reflexões.
Em minha experiência, o Grok supera o ChatGPT na geração de imagens e na citação de fontes, enquanto o ChatGPT leva a melhor em precisão e simplicidade nas respostas.
Esses pontos refletem não apenas as prioridades de design de cada IA, mas também o tempo de desenvolvimento e os objetivos de suas respectivas empresas criadoras.
A OpenAI, por trás do ChatGPT, focou em refinamento conversacional, enquanto a xAI, com o Grok, parece investir em funcionalidades adicionais, como a criação de conteúdo visual.
### Minha opinião

Não há um vencedor absoluto entre Grok e ChatGPT – a escolha depende do que você precisa. Se seu foco é geração de imagens ou rastreamento de fontes, o Grok pode ser a melhor opção. Se busca respostas rápidas e assertivas, o ChatGPT provavelmente atenderá melhor.
Ambas as IAs são ferramentas incríveis, e o mais fascinante é ver como elas continuam evoluindo, moldando o futuro da interação entre humanos e máquinas.
-

@ 9e69e420:d12360c2
2025-02-14 18:07:10
Vice President J.D. Vance addressed the Munich Security Conference, criticizing European leaders for undermining free speech and traditional values. He claimed that the biggest threat to Europe is not from external enemies but from internal challenges. Vance condemned the arrest of a British man for praying near an abortion clinic and accused European politicians of censorship.
He urged leaders to combat illegal immigration and questioned their democratic practices. “There is a new sheriff in town,” he said, referring to President Trump. Vance's remarks were unexpected, as many anticipated discussions on security or Ukraine. His speech emphasized the need for Europe to share the defense burden to ensure stability and security.
-

@ 866e0139:6a9334e5
2025-03-31 19:38:39
 
***
**Autor:** **[Carlos A. Gebauer.](https://make-love-not-law.com/lebenslauf.html)** *Dieser Beitrag wurde mit dem **[Pareto-Client](https://pareto.space/read)** geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden **[hier.](https://pareto.space/read?category=friedenstaube)***
***
Am 18. März 1924 schenkte meine Großmutter ihren Töchtern einen kleinen Bruder. Weil sein Vater fürchtete, der Junge könnte unter seinen vier Schwestern verweichlichen, schickte er den Kleinen zu Wochenendfreizeiten einer örtlichen Pfadfindergruppe. Ein Weltkriegsveteran veranstaltete dort mit den Kindern Geländespiele quer durch die schlesischen Wälder. Man lernte, Essbares zu finden, Pilze zu bestimmen, sich im Freien zu orientieren und Feuer zu machen.
Bald wurde deutlich, dass der Heranwachsende auch nicht mehr in den Blockflötenkreis seiner Schwestern und ihrer Freundinnen passte. Das Umfeld befürwortete, sein besonderes musikalisches Talent auf das Klavierspiel und das Flügelhorn zu richten. Kontakte bei der anschließenden Kirchenmusik mündeten schließlich in den elterlichen Entschluss, den nun 14-jährigen in ein Musikschulinternat zu schicken.
### Es begann der Zweite Weltkrieg
Ein Jahr später, das erste Heimweh hatte sich langsam beruhigt, änderten sich die Verhältnisse schlagartig. Es begann der Zweite Weltkrieg. Mitschüler unter den jungen Musikern erfuhren, dass ihre älteren Brüder nun Soldaten werden mussten. Noch hielt sich die Gemeinschaft der jetzt 15-jährigen im Internat aber an einer Hoffnung fest: Bis sie selbst in das wehrfähige Alter kommen würden, müsste der Krieg längst beendet sein. In dieser Stimmungslage setzten sie ihre Ausbildung fort.
Es kam anders. Für den 18-jährigen erfolgte die befürchtete Einberufung in Form des „Gestellungsbefehls“. Entsprechend seiner Fähigkeiten sah man ihn zunächst für ein Musikkorps vor und schickte ihn zu einer ersten Grundausbildung nach Südfrankreich. Bei Nizza fand er sich nun plötzlich zwischen Soldaten, die Handgranaten in das Mittelmeer warfen, um Fische zu fangen. Es war das erste Mal, dass er fürchtete, infolge Explosionslärms sein Gehör zu verlieren. In den kommenden Jahren sollte er oft die Ohren zu- und den Mund offenhalten müssen, um sich wenigstens die Möglichkeit der angezielten Berufsausübung zu erhalten – wenn es überhaupt je dazu kommen würde.
***
**DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!**
***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos* ***[hier](https://pareto.space/a/naddr1qqsxydty8qek2wpsvyck2wphxajrvefjvesngcfhxenrgdty89nrzvgzyzrxuqfepp2e79w9aluaz2252vyz7qdpld05pgjmeurhdgm2jv6w2qcyqqq823cpp4mhxue69uhkummn9ekx7mqprpmhxue69uhkummnw3ezuurpwfjhgmewwdcxzcm9qythwumn8ghj7mn0wd68ytnsv9ex2ar09e6x7amwqyf8wumn8ghj7mmxve3ksctfdch8qatzqythwumn8ghj7urpwfjhgmewdehhxarjxyhxxmmdszcvqk)*** *oder am Ende des Textes.*
***
Schon nach kurzer Zeit änderte sich die Befehlslage wieder. Der Musikstudent wurde nun zum Infanteristen und nach Russland an die Front verbracht. Vor ihm lagen jetzt drei Kriegsjahre: Gewalt, Dreck, Gewehrkugeln, Panzerschlachten, Granatsplitter, Luftangriffe, Entbehrungen, Hunger, Kälte, sieben Verwundungen, Blut und Schmerzen, Sterbende überall, Tote, Schreiende. Verzweiflung. Sorgen. Ängste. Todesangst. Zurückweichen? Verboten! Und die stets klare Ansage dazu: Wer nicht da vorne gegen den Feind um sein Leben kämpft, dem wird es ganz sicher da hinten von den eigenen Kameraden genommen.
Ein gewährter Fronturlaub 1944 versprach glückliche Momente. Zurück zu den Eltern, zurück zu den Schwestern, zurück nach Freiburg. Doch die Familie war nicht zu Hause, die Türen verschlossen. Eine Nachbarin öffnete ihr Fenster und rief dem Ratlosen zu: „Beeil‘ dich! Renn‘ zum Friedhof. Der Vater ist tot. Sie sind alle bei der Beerdigung!“ Wieder hieß es, qualvoll Abschied nehmen. Zurück an die Front.
Nach einem weiteren russischen Winter brach sich unübersehbar die Erkenntnis Bahn, dass der Krieg nun seinem Ende zugehe. Doch das Bemühen im Rückzug, sich mit einem versprengten Haufen irgendwie Richtung Heimat orientieren zu können, wurde doppelt jäh unterbrochen. Fanatische Vorgesetzte befahlen die längst Geschlagenen wieder gen Osten. Kurz darauf fielen sie heranrückenden russischen Truppen in die Hände.
### Kriegsgefangenschaft: Tabakration gegen Brot
Drei Jahre dem Tod entgangen, schwer verletzt und erschöpft war der 21-jährige also nun ein Kriegsgefangener. Jetzt lagen drei Jahre russischer Kriegsgefangenschaft vor ihm. Ständig war unklar, wie es weiterginge. Unmöglich jedenfalls, sich noch wie ein Pfadfinder aus den Wäldern zu ernähren. Es begannen die Jahre des Schlafens auf Brettern, die Zeit der ziellosen Zugtransporte an unbekannte Orte. Niemand sprach. Nur der Sonnenstand machte klar: Es ging nie Richtung Heimat, sondern immer weiter nach Osten. Weil der Blechbläser nicht rauchte, konnte er seine Tabakration gegen Brot tauschen. So überlebte er auch die Zeit des Hungers und der Morde in den Lagern, die Horrorbilder der nachts Erschlagenen und in die Latrinen geworfenen Toten, der sinnlosen Zwangsarbeiten und der allgegenwärtigen Wanzen. Wer versuchte zu fliehen, der wurde erschossen und sein Körper zur Abschreckung in den Fangdrähten belassen. Im Sommer stanken die dort verwesenden Leichen, wenn nicht Vögel sie rechtzeitig gefressen hatten.
Als der 24-jährige schließlich sechs Jahre nach seiner Einberufung aus russischer Kriegsgefangenschaft entlassen wurde, gab es kein Zurück mehr in seine schlesische Heimat. Abgemagert reiste er der vertriebenen Mutter nach, die mit seinen Schwestern und Millionen anderen Flüchtlingen im Westen Deutschlands verteilt worden war. Kraft Ordnungsverfügung wohnte sie jetzt im sauerländischen Bad Laasphe in einem schimmligen Garagenanbau. Als ihn ein Passant auf dieser Reise morgens allein, nur mit einem Becher an der Schnur um den Hals, auf Krücken durch Berlin ziehen sah, gab er ihm schweigend sein Butterbrot.
Der kleine, sanfte Junge aus dem schlesischen Freiburg hat danach noch 60 Jahre gelebt. Es dauerte zunächst sechs Jahre, bis er wieder kräftig genug war, ein Instrument zu spielen. 30-jährig saß er dann endlich in einem Orchester und begann ein normales Berufsleben. Aber sein Körper und seine Seele waren für immer aus jeder Normalität gerissen.
Irgendwo in Russland war ihm die linke Hüfte so versteift worden, dass sich seine Beine im Liegen an Wade und Schienbein überkreuzten. Er musste also stets den Oberkörper vorbeugen, um überhaupt laufen zu können. Über die Jahrzehnte verzog sich so sein gesamter Knochenbau. Jeder Tag brachte neue orthopädische Probleme und Schmerzen. Ärzte, Masseure, Physiotherapeuten, Schmerzmittel und Spezialausrüstungen aller Art prägten die Tagesabläufe. Asymmetrisch standen seine Schuhe nebeneinander, die ein Spezialschuster ihm mit erhöhter Sohle und Seitenstabilisierung am Knöchel fertigte. Sessel oder Sofas waren ihm nicht nutzbar, da er nur auf einem Spezialstuhl mit halb abgesenkter Sitzfläche Ruhe fand. Auf fremden Stühlen konnte er nur deren Vorderkante nutzen.
### "In den Nächten schrie er im Schlaf"
Und auch wenn er sich ohne Krankheitstage bis zuletzt durch seinen Berufsalltag kämpfte, so gab es doch viele Tage voller entsetzlicher Schmerzen, wenn sich seine verdrehte Wirbelsäule zur Migräne in den Kopf bohrte. Bei alledem hörte man ihn allerdings niemals über sein Schicksal klagen. Er ertrug den ganzen Wahnsinn mit einer unbeschreiblichen Duldsamkeit. Nur in den Nächten schrie er bisweilen im Schlaf. In einem seiner Alpträume fürchtete er, Menschen getötet zu haben. Aber auch das erzählte er jahrzehntelang einzig seiner Frau.
Als sich einige Jahre vor seinem Tod der orthopädische Zustand weiter verschlechterte, konsultierte er einen Operateur, um Entlastungsmöglichkeiten zu erörtern. Der legte ihn auf eine Untersuchungsliege und empfahl, Verbesserungsversuche zu unterlassen, weil sie die Lage allenfalls verschlechtern konnten. In dem Moment, als er sich von der Liege erheben sollte, wurde deutlich, dass ihm dies nicht gelang. Die gereichte Hand, um ihn hochzuziehen, ignorierte er. Stattdessen rieb er seinen Rumpf ganz alleine eine quälend lange Minute über die Fläche, bis er endlich einen Winkel fand, um sich selbst in die Senkrechte zu bugsieren. Sich nicht auf andere verlassen, war sein Überlebenskonzept. Jahre später, als sich sein Zustand noch weiter verschlechtert hatte, lächelte er über seine Behinderung: „Ich hätte schon vor 60 Jahren tot auf einem Acker in Russland liegen können.“ Alles gehe irgendwann vorbei, tröstete er sich. Das war das andere Überlebenskonzept: liebevoll, friedfertig und sanft anderen gegenüber, unerbittlich mit sich selbst.
Sechs Monate vor seinem Tod saß er morgens regungslos auf seinem Spezialstuhl. Eine Altenpflegerin fand ihn und schlug Alarm. Mit allen Kunstgriffen der medizinischen Technik wurde er noch einmal in das Leben zurückkatapultiert. Aber seine Kräfte waren erschöpft. Es schob sich das Grauen der Vergangenheit zwischen ihn und die Welt. Bettlägerig kreiste er um sich selbst, erkannte niemanden und starrte mit weit offenen Augen an die Decke. „Die Russen schmeißen wieder Brandbomben!“, war einer seiner letzten Sätze.
Der kleine Junge aus Schlesien ist nicht zu weich geraten. Er hat sein Leid mit unbeugsamer Duldsamkeit ertragen. Er trug es wohl als Strafe für das Leid, das er anderen anzutun genötigt worden war. An seinem Geburtstag blühen immer die Magnolien. In diesem Jahr zum hundertsten Mal.
*Dieser Text wurde am 23.3.2024 erstveröffentlicht auf* *[„eigentümlich frei“.](https://ef-magazin.de/2024/03/23/21072-make-love-not-law-kriegstuechtig)*
***
*Carlos A. Gebauer studierte Philosophie, Neuere Geschichte, Sprach-, Rechts- und Musikwissenschaften in Düsseldorf, Bayreuth und Bonn. Sein juristisches Referendariat absolvierte er in Düsseldorf, u.a. mit Wahlstationen bei der Landesrundfunkanstalt NRW, bei der Spezialkammer für Kassenarztrecht des Sozialgerichtes Düsseldorf und bei dem Gnadenbeauftragten der Staatsanwaltschaft Düsseldorf.*
*Er war unter anderem als Rechtsanwalt und Notarvertreter bis er im November 2003 vom nordrhein-westfälischen Justizministerium zum Richter am Anwaltsgericht für den Bezirk der Rechtsanwaltskammer Düsseldorf ernannt wurde. Seit April 2012 arbeitet er in der Düsseldorfer Rechtsanwaltskanzlei Lindenau, Prior & Partner. Im Juni 2015 wählte ihn die Friedrich-August-von-Hayek-Gesellschaft zu ihrem Stellvertretenden Vorsitzenden. Seit Dezember 2015 ist er Richter im Zweiten Senat des Anwaltsgerichtshofes NRW.*
*1995 hatte er parallel zu seiner anwaltlichen Tätigkeit mit dem Verfassen gesellschaftspolitischer und juristischer Texte begonnen. Diese erschienen seither unter anderem in der Neuen Juristischen Wochenschrift (NJW), der Zeitschrift für Rechtspolitik (ZRP) in der [Frankfurter Allgemeinen Zeitung](http://www.faz.de/), der [Freien Presse Chemnitz](http://www.freiepresse.de/), dem „Schweizer Monat“ oder dem Magazin für politische Kultur CICERO. Seit dem Jahr 2005 ist Gebauer ständiger Kolumnist und Autor des Magazins „eigentümlich frei“.*
*Gebauer glaubt als puristischer Liberaler unverbrüchlich an die sittliche Verpflichtung eines jeden einzelnen, sein Leben für sich selbst und für seine Mitmenschen verantwortlich zu gestalten; jede Fremdbestimmung durch Gesetze, staatliche Verwaltung, politischen Einfluss oder sonstige Gewalteinwirkung hat sich demnach auf ein ethisch vertretbares Minimum zu beschränken. Die Vorstellung eines europäischen Bundesstaates mit zentral detailsteuernder, supranationaler Staatsgewalt hält er für absurd und verfassungswidrig.*
\
**Aktuelle Bücher:**
Hayeks Warnung vor der Knechtschaft (2024) – [hier im Handel](https://www.buchkomplizen.de/hayeks-warnung-vor-der-knechtschaft.html?listtype=search\&searchparam=Carlos%2520A%2520gebauer)
Das Prinzip Verantwortungslosigkeit (2023) – [hier im Handel](https://www.buchkomplizen.de/das-prinzip-verantwortungslosigkeit.html?listtype=search\&searchparam=Carlos%2520A%2520gebauer)
***
**LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!**
***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.*
Schon jetzt können Sie uns unterstützen:
* Für **50 CHF/EURO** bekommen Sie ein Jahresabo der Friedenstaube.
* Für **120 CHF/EURO** bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
* Für **500 CHF/EURO** werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
* Ab **1000 CHF** werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
**Für Einzahlungen in CHF (Betreff: Friedenstaube):**
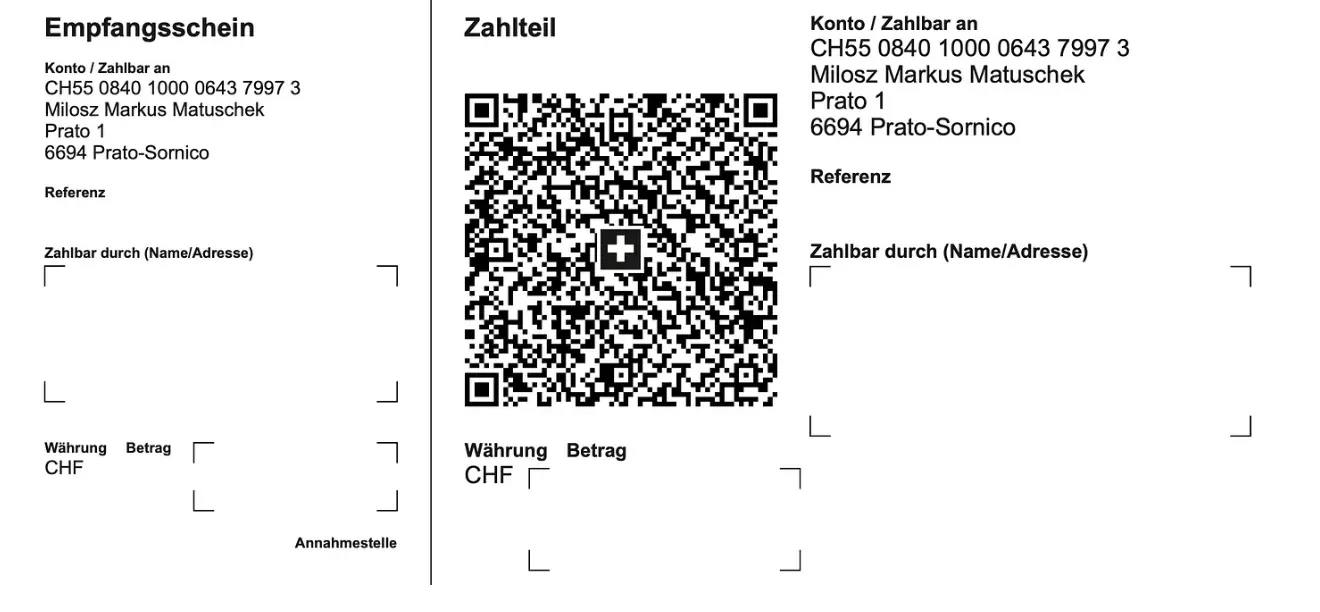
**Für Einzahlungen in Euro:**
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
**Betreff: Friedenstaube**
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: <milosz@pareto.space>
***
**Sie sind noch nicht auf** [Nostr](https://nostr.com/) **and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil!** Erstellen Sie sich einen Account auf [Start.](https://start.njump.me/) Weitere Onboarding-Leitfäden gibt es im [Pareto-Wiki.](https://wiki.pareto.space/de/home)
-

@ 2e8970de:63345c7a
2025-03-31 19:08:11
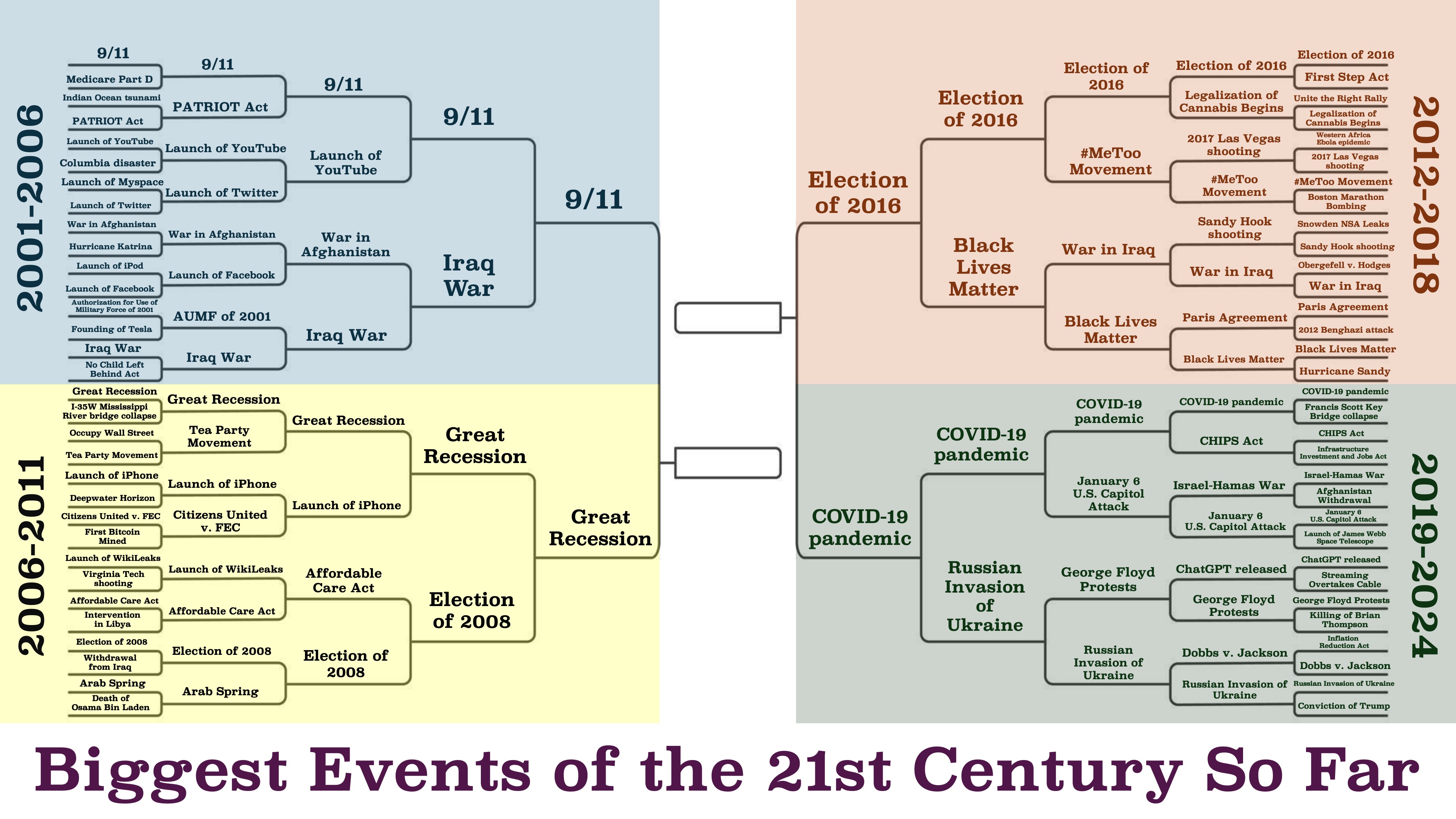
https://x.com/beatmastermatt/status/1906329250115858750
originally posted at https://stacker.news/items/930491
-

@ e3ba5e1a:5e433365
2025-02-13 06:16:49
My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get [this line](https://www.youtube.com/shorts/kqsomjpz7ok):
“Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.”
Yesterday, I came across a comment on the song [Devil Went Down to Georgia](https://youtu.be/ut8UqFlWdDc) that had a very similar feel to it:

America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans.
That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form.
For most countries, saying “our nation is the greatest” *is*, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people *should* be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence.
But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America.
That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is *freedom*. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit.
American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are *definitionally* better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.)
In *Devil Went Down to Georgia*, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.”
*Libertas magnitudo est*
-

@ bcbb3e40:a494e501
2025-03-31 16:00:24
|[](https://amzn.to/4jaGBZ4)|
|:-:|
|[WAJDA, Andrzej; _Cenizas y diamantes_, 1958](https://amzn.to/4jaGBZ4)|
Presentamos una nueva reseña cinematográfica, y en esta ocasión hemos elegido «Cenizas y diamantes», una película polaca del célebre y prolífico director **Andrzej Wajda** (1926-2016), estrenada en el año 1958. Se trata de uno de los grandes clásicos del cine polaco. El filme refleja una etapa dramática desde la perspectiva histórica para la nación polaca, como es el final de la Segunda Guerra Mundial, a raíz de la capitulación alemana del 8 de mayo de 1945. El contexto en el que se desarrolla se ambienta en la celebración del final de la guerra con el aplastante triunfo de la URSS, con las tropas soviéticas ocupando toda la Europa oriental, y en particular Polonia, que vive un momento de oscuridad e incertidumbre. El protagonista, **Maciek Chełmicki** (interpretado magistralmente por **Zbigniew Cybulski** (1927-1967), apodado el «James Dean polaco»), es un joven nacionalista polaco, de orientación anticomunista, que se ve implicado en un complot urdido para asesinar a un líder comunista local. Maciek opera desde la clandestinidad, bajo el grupo **Armia Krajowa (AK)**, el Ejército Nacional polaco, una organización de resistencia, primero contra los alemanes y, posteriormente, contra los soviéticos. Durante el metraje, se plantea una dicotomía permanente entre la libertad entendida como la defensa de la soberanía de Polonia, desde posturas nacionalistas, y quienes consideran la ocupación soviética como algo positivo. Estas circunstancias atrapan al protagonista, que se ve envuelto en una espiral de violencia y traición.
Maciek Chełmicki, nuestro protagonista, cuenta con todas [las características del héroe trágico](https://hiperbolajanus.com/posts/caballero-muerte-diablo-jean-cau/), pues tiene en sus manos una serie de acciones que comprometen el futuro de un pueblo, que consiste en cumplir la misión que le ha sido encomendada, pero en su camino se cruza una joven, Krystyna, una joven camarera de un hotel de la que se enamora en ese mismo día. Este último hecho sirve de punto de partida para todas las dudas, dilemas y dicotomías a las que hacemos referencia. Hay un dilema moral evidente en un mundo en ruinas, [devastado por la guerra, la muerte y el nihilismo](https://hiperbolajanus.com/posts/en-el-mar-de-la-nada-curzio-nitoglia/). En este sentido Wajda nos muestra un lenguaje cinematográfico muy evidente, a través de una técnica expresionista muy depurada, con el uso del blanco y negro, los contrastes generados por las sombras y la atmósfera opresiva que transmite angustia, desesperación y vulnerabilidad de los protagonistas. Además también destilan una fuerte carga emocional, donde no están exentos elementos poéticos y un poderoso lirismo.
||
|:-:|
|Maciek Chełmicki, el protagonista.|
Hay elementos simbólicos que no podemos obviar, y que contribuyen a consolidar el análisis que venimos haciendo, como, por ejemplo, la estética del protagonista, con unas gafas oscuras, que actúan como una suerte de barrera frente al mundo que le rodea, como parte del anonimato tras el cual el joven Maciek vive de forma introspectiva su propio drama particular y el de toda una nación.
|[](https://www.hiperbolajanus.com/libros/mar-nada-curzio-nitoglia/)|
|:-:|
|[NITOGLIA, Curzio; _En el mar de la nada: Metafísica y nihilismo a prueba en la posmodernidad_; Hipérbola Janus, 2023](https://www.hiperbolajanus.com/libros/mar-nada-curzio-nitoglia/)|
Hay una escena especialmente poderosa, y casi mítica, en la que los dos jóvenes protagonistas, Maciek y Krystina, se encuentran entre las ruinas de una Iglesia, en la que se destaca en primer plano, ocupando buena parte de la pantalla, la imagen de un Cristo invertido sobre un crucifijo, donde también se encuentran dos cuerpos colgados hacia abajo en una estampa que refleja la devastación moral y espiritual de toda una época. De hecho, [la imagen del crucifijo invertido refleja el máximo punto de subversión y profanación de lo sagrado](https://hiperbolajanus.com/posts/la-cruz-frente-la-modernidad/), y que en el caso concreto de la película viene a representar la destrucción del orden moral y de valores cristianos que la propia guerra ha provocado. Polonia es una nación profundamente católica, convertida al Cristianismo en el 966 a raíz de la conversión del príncipe **Miecislao I**, contribuyendo de manera decisiva a la formación de la identidad nacional polaca. El catolicismo siempre ha sido un medio de cohesión y defensa frente a las influencias extranjeras y la ocupación de terceros países, una constante en la historia del país, como el que ilustra la propia película con la URSS. En este sentido, la imagen de una Iglesia en ruinas, el lugar donde se encuentra representado el principio de lo sagrado e inviolable, [supone una forma de perversión de todo principio de redención y salvación frente a la tragedia](https://hiperbolajanus.com/posts/mas-nos-vale-rezar/), y al mismo tiempo viene a significar que la Tradición ha sido abandonada y pervertida. En la misma línea, el protagonista, Maciek, se encuentra atrapado en una espiral de violencia a través de sus actos terroristas perpetrados contra la autoridad soviética que ocupa su país. Los dos cuerpos anónimos que cuelgan boca abajo, de forma grotesca, también participan de este caos y desequilibrio de un orden dislocado, son parte de la deshumanización y el nihilismo que todo lo impregna.
||
|:-:|
|Maciek y Krystina en una iglesia en ruinas|
Como ya hemos mencionado, la película se encuentra plagada de paradojas y dicotomías, en las que nuestro protagonista, [el joven rebelde e inconformista](https://hiperbolajanus.com/posts/juventud-contestacion/), debe elegir permanentemente, en unas decisiones que resultan trascendentales para su futuro y el de la propia nación. La figura femenina que irrumpe en su vida, y que representa un principio disruptivo que provoca una fractura interior y una crisis, le suscita una toma de conciencia de su propia situación y le fuerza a tomar un camino entre la «felicidad», del «amor», la «esperanza» y la «vida», que le permita superar la deriva nihilista y autodestructiva de la lucha clandestina, la cual le aboca a un destino trágico (que no vamos a desentrañar para no hacer spoiler). En relación al propio título de la película, «Cenizas y diamantes», basada en el poema del poeta y dramaturgo polaco **Cyprian Norwid** (1821-1883) y en la novela del autor, también polaco, **Jerzy Andrzejewski** (1909-1983), nos destaca la dualidad de los dos elementos que lo componen, y que definen el contraste entre el mundo sombrío y oscuro (Cenizas) y la esperanza y la luz que representa susodicha figura femenina (diamantes). La segunda alternativa parece un imposible, una quimera irrealizable que se pliega ante un Destino implacable, irreversible y cruel.
En consecuencia, y a la luz de los elementos expuestos, podemos decir que se nos presentan dilemas propios de la filosofía existencialista, que conoce su punto álgido en esos años, con autores como **Jean Paul Sartre** (1905-1980), **Albert Camus** (1913-1960), **Karl Jaspers** (1883-1969) o [**Martin Heidegger**](https://amzn.to/4cmjvwE) (1889-1976) entre otros. Respecto a éste último, a Heidegger, podemos encontrar algunas claves interesantes a través de su filosofía en relación al protagonista, a Maciek, especialmente a través de la idea del *Dasein*, a la idea de haber sido arrojado al mundo (*Geworfenheit*), y la manera tan extrema y visceral en la que vive susodicha condición. Todos aquellos elementos que dan sentido a la vida colectiva [se encuentran decaídos o destruidos en su esencia más íntima, la Patria, la religión o la propia idea de Comunidad orgánica](https://hiperbolajanus.com/posts/textos-tradicion-tiempos-oscurecimiento-hj/). De modo que el protagonista se ha visto «arrojado» frente a una situación o destino indeseado, en unas coyunturas totalmente desfavorables en las que no queda otra elección. Sus decisiones están permanentemente condicionadas por la circunstancia descrita y, por tanto, vive en un mundo donde no controla nada, en lugar de ser sujeto es un mero objeto transportado por esas circunstancias ajenas a su voluntad. Sin embargo, y en coherencia con el *Dasein* heideggeriano, vemos como Maciek, a raíz de conocer a Krystyna, comienza a experimentar una catarsis interior, que muestra por momentos el deseo de superar ese «ser arrojado al mundo contra tu voluntad», trascendiendo esa condición absurda e irracional de unas decisiones enajenadas de su voluntad para dotar de una significación y un sentido la propia existencia.
||
|:-:|
|Andrzej Wajda, el director de la película.|
Otro elemento característico de la filosofía heideggeriana lo podemos encontrar en la «angustia» (*angst*) a través de la ausencia de un sentido y fundamento último que justifique la existencia del protagonista. Es una angustia en a que el *Dasein* se enfrenta a la «nada», a ese vacío existencial que hace inútil toda la lucha que Maciek lleva a cabo en la clandestinidad, con asesinatos y actos de terrorismo que pretenden salvaguardar algo que ya no existe, y que simboliza muy bien la Iglesia en ruinas con sus símbolos religiosos invertidos de la que hablábamos con anterioridad. Recuerda un poco a esa dicotomía que se plantea entre ser conservador o reaccionario frente a una realidad como la del propio presente, en la que los valores tradicionales han sido totalmente destruidos, y más que conservar se impone la reacción para volver a construir de la nada.
|[](https://www.hiperbolajanus.com/libros/textos-tradicion-tiempos-oscurecimiento-hiperbola-janus/)|
|:-:|
|[Hipérbola Janus; _Textos para la Tradición en tiempos del oscurecimiento: Artículos publicados entre 2014 y 2019 en hiperbolajanus.com_; Hipérbola Janus, 2019](https://www.hiperbolajanus.com/libros/textos-tradicion-tiempos-oscurecimiento-hiperbola-janus/)|
Todas las dudas que asaltan al protagonista se ven incrementadas en el momento decisivo, cuando se dispone a dar muerte al líder comunista. Se produce una tensión interna en Maciek, que se encuentra ligado a la joven que ha conocido ese día, y en ella es donde encuentra ese leve destello de humanidad. Esa circunstancia le hace replantearse por un instante el cumplimiento de su misión, pero es un dilema que no tiene salida, y por ello le asalta nuevamente la angustia frente a esa «nada», ese mundo vacío e incomprensible que trasciende el marco de sus propias elecciones.
Uno de los conceptos centrales de Heidegger en [*Ser y tiempo*](https://amzn.to/4l7uMoi) es el *Sein-zum-Tode* (*ser-para-la-muerte*), la idea de que la muerte es la posibilidad más propia y definitiva del *Dasein*, y que enfrentarla auténticamente permite vivir de manera más plena. Y es que el protagonista se encuentra permanentemente sobre esa frontera entre la vida y la muerte, que afronta con todas sus consecuencias, conscientemente, y la acepta. Esta actitud podría leerse como una forma de *Dasein* inauténtico, una huida del *ser-para-la-muerte* mediante la distracción (*das Man*, el «se» impersonal). Sin embargo, su decisión de cumplir la misión sugiere un enfrentamiento final con esa posibilidad. Otro aspecto que podemos conectar con el pensamiento heideggeriano es la autenticidad o inautenticidad de la vida del protagonista. En relación a la inautenticidad vemos como al principio sigue las órdenes de sus superiores en la organización sin cuestionarlas, lo cual implica un comportamiento inequívocamente alienante. Respecto a aquello que resulta auténtico de su existencia son sus relaciones con Krystyna, que supone imponer su propia voluntad y decisión, mostrando un *Dasein* que asume su libertad.
||
|:-:|
|Escena de la película.|
Otros aspectos más generales de la filosofía existencialista redundan sobre estos mismos aspectos, con la elección entre la libertad absoluta y la condena inevitable. La idea del hombre condenado a actuar, a una elección continua, aún cuando el hombre no es dueño de su destino, o las consecuencias de tales acciones son absurdas, irracionales e incomprensibles. El propio absurdo de la existencia frente al vacío y la ausencia de principios sólidos en los que cimentar la vida, no solo en sus aspectos cotidianos más básicos, sino en aquellos más profundos de la existencia. La soledad y la propia fatalidad frente a un Destino que, como ya hemos apuntado anteriormente, parece imponerse de manera irrevocable, y podríamos decir que brutalmente, al individuo aislado, incapaz de asirse en una guía, en unos valores que le permitan remontar la situación.
En términos generales «Cenizas y diamantes», además de ser una película de gran calidad en sus aspectos técnicos, en su fotografía, en la configuración de sus escenas y en el propio desarrollo argumental, bajo un guión espléndidamente ejecutado a lo largo de sus 98 minutos de duración, también nos invita a una reflexión profunda sobre la condición humana y la propia Modernidad. Y es algo que vemos en nuestros días, con las consecuencias de un pensamiento débil, con la promoción del individualismo, el hedonismo y lo efímero. La ausencia de estructuras sólidas, [la subversión de toda forma de autoridad y jerarquía tradicionales](https://hiperbolajanus.com/posts/metapolitica-tradicion-modernidad-antologia-julius-evola/). Paradójicamente, el mundo actual tiende a formas de poder y autoridad mucho más invasivas y coercitivas, tanto a nivel individual como colectivo, pero en la misma línea abstracta e impersonal que nos describe la película, abocándonos a la alienación y la inautenticidad de nuestras propias vidas. Y como Maciek, también nosotros, vivimos en un mundo dominado por la incertidumbre y la desesperanza, en el que el globalismo y sus perversas ideologías deshumanizantes actúan por doquier.
||
|:-:|
|Carátula original de la película en polaco.|
---
**Artículo original**: Hipérbola Janus, [_Reseña de «Cenizas y Diamantes» (Andrzej Wajda, 1958)_](https://www.hiperbolajanus.com/posts/resena-cenizas-diamantes/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/resena-cenizas-diamantes/), 31/Mar/2025
-

@ daa41bed:88f54153
2025-02-09 16:50:04
There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy [article on the pros of a strategic Bitcoin reserve](https://geek.npub.pro/post/dxqkgnjplttkvetprg8ox/), I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
**Nostr** is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
**Zap** is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what [Lightning](https://lightning.network/) or [Cashu](https://cashu.space/) are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-

@ e3ba5e1a:5e433365
2025-02-05 17:47:16
I got into a [friendly discussion](https://x.com/snoyberg/status/1887007888117252142) on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
* Unlike full single payer, individuals incur high costs
* Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
* Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
* Reduce regulations significantly.
* In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
1. Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
2. Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-

@ bcbb3e40:a494e501
2025-03-31 15:44:56
El 7 de febrero de 2025, Donald Trump firmó una orden ejecutiva que establecía una «Oficina de la Fe» en la Casa Blanca, dirigida por su asesora espiritual Paula White-Cain, la pastora de esa «teología de la prosperidad» (*prosperity theology*) que predica el «Evangelio de la salud y la riqueza» (*health and wealth gospel[^1]*). Investida de su nueva función, la reverenda pastora dijo: «Tengo la autoridad para declarar a la Casa Blanca un lugar santo. Es mi presencia la que la santifica»[^2]. Los siete rabinos del «Sanedrín Naciente» —la corte suprema que guiará a Israel cuando se reconstruya el Templo de Jerusalén— enviaron conmovedoras felicitaciones al presidente Trump por el establecimiento de esta Oficina. «Expresamos nuestra sincera gratitud —se lee en el mensaje oficial enviado a Trump desde el Monte Sión— por llevar la fe a la vanguardia de la cultura estadounidense y mundial mediante el establecimiento de la Oficina de la Fe en la Casa Blanca. Su reconocimiento de la importancia de la religión en la vida pública es un paso hacia [la restauración de los valores morales y del liderazgo espiritual en el mundo](https://www.hiperbolajanus.com/posts/patriots-mutti/)[^3]. La carta del «Sanedrín Naciente», que augura el éxito a la «misión divina» del presidente estadounidense, reproduce las dos caras de una «moneda del Templo», acuñada en 2017 para celebrar el traslado de la embajada estadounidense a Jerusalén y, simultáneamente, el centenario de la Declaración Balfour. En el anverso se ven los perfiles de Donald Trump y Ciro el Grande, a quien la tradición judía atribuye la reconstrucción del templo destruido por los babilonios, con la inscripción (en hebreo e inglés) «*Cyrus —Balfour— Trump Declaration 1917-2017*»; en el reverso está la imagen del Templo de Jerusalén[^4]. Otra moneda, que lleva los perfiles de Trump y Ciro en el anverso y los de Trump y Netanyahu en el reverso, fue acuñada en 2018 para celebrar el septuagésimo aniversario de la independencia del «Estado de Israel»; se observa dos inscripciones en hebreo e inglés: «Y Él me encargó construirle una casa en Jerusalén» y «Guerra de los Hijos de la Luz contra los Hijos de las Tinieblas».
El tema de la «guerra de los Hijos de la Luz contra los Hijos de las Tinieblas» ha tenido una difusión particular en el imaginario y la propaganda trumpista. El 7 de junio de 2020, monseñor Carlo Maria Viganò, ex nuncio de la Santa Sede en los Estados Unidos, escribió una carta al presidente Donald Trump que comenzaba así: «Estamos asistiendo en los últimos meses a la formación de dos bandos, que los definiría bíblicos: los hijos de la luz y los hijos de las tinieblas»[^5]. El 1 de enero de 2021, el agitprop estadounidense Steve Bannon declaró en una entrevista con Monseñor Viganò: «Esta es una batalla de época entre los hijos de la Luz y los hijos de las Tinieblas»[^6].
Son numerosos los judíos sionistas que están en el círculo del presidente Trump: además de su hija Ivanka (convertida en 2009) y su yerno Jared Kushner (entonces Consejero Anciano del Presidente), el 19 de noviembre de 2024 el «The Jerusalem Post»[^7] publicó una lista de los más influyentes: Stephen Miller, subdirector del *staff* de la Casa Blanca y consejero de Seguridad Nacional de Estados Unidos; David Melech Friedman, a quien en 2016 Trump nombró embajador en Israel; el multimillonario «filántropo» Steven Charles Witkoff, enviado especial de Estados Unidos a Oriente Medio; Miriam Adelson, directora del periódico «Israel Hayom», clasificada por *Bloomberg Billionaires* como la quinta mujer más rica del mundo (con un patrimonio neto de 32,400 millones de dólares), financiadora de iniciativas políticas conservadoras en Estados Unidos e Israel; el banquero Boris Epshteyn, consejero estratégico de la campaña presidencial de Trump en 2020; Howard Williams Lutnick, presidente de la *Cantor Fitzgerald* del *Grupo BGC*, financista de las campañas presidenciales de Donald Trump en 2020 y 2024, ahora secretario de Comercio; la modelo Elizabeth Pipko, portavoz nacional del Partido Republicano y creadora de un «museo interactivo virtual» sobre la «Shoah» como parte del proyecto de *Lest People Forget*, cuyo objetivo es combatir el «antisemitismo» y la «negacionismo»; Lee Michael Zeldin, miembro republicano de la Cámara de Representantes por el estado de Nueva York del 2015 al 2023 y actualmente administrador de la EPA (*Environmental Protection Agency*); la columnista Laura Elizabeth Loomer, «orgullosamente islamófoba», activa patrocinadora de Trump en la campaña para las elecciones presidenciales de 2024; Sidney Ferris Rosenberg, influyente presentador de radio y periodista deportivo; William Owen Scharf, Asistente del Presidente y secretario del personal de la Casa Blanca; Marc Jeffrey Rowan, «filántropo» con un patrimonio neto valorado por *Forbes* en ocho mil ochocientos millones de dólares.
Además de estos, cabe mencionar al popular presentador de radio Mark Levin quien, en diciembre de 2019, durante la celebración de la fiesta de Janucá en la Casa Blanca, saludó a Donald Trump como «el primer presidente judío de los Estados Unidos»[^8]. Según un funcionario de alto nivel de la Casa Blanca, Donald Trump se convirtió al judaísmo dos años antes en la sinagoga de la secta Jabad Lubavitch en la ciudad de Nueva York. David Elias Goldberg, miembro del *Jewish Center of Antisemitic Study*, también entrevistó al funcionario, para quien «Trump fue “instado” por su hija Ivanka y su yerno Jared Kushner para abrazar la fe. Inicialmente, Trump se habría mostrado reacio, considerando que esto podría enfriar el apoyo del electorado evangélico». Luego, informa «Israel Today News», «cambió de opinión y se convirtió oficialmente a principios de 2017. La ceremonia se llevó a cabo en privado y se guardó celosamente durante casi dos años»[^9]. Pero ya en septiembre de 2015, el rabino millonario Kirt Schneider, invitado a la Trump Tower de Nueva York, había impuesto sus manos sobre la cabeza de Donald Trump y lo había bendecido en hebreo e inglés, declarando: «Las únicas dos naciones que tienen una relación privilegiada con Dios son Israel y los Estados Unidos de América»[^10].
El 7 de octubre de 2024, en el aniversario de la operación de Hamas «Diluvio de Al-Aqsa», Trump fue acompañado por un «superviviente de la Shoah» a la tumba de Menachem Mendel Schneerson, séptimo y último Rabino de los *Hasidim* de la secta Jabad Lubavitch, que en 1991 declaró a sus seguidores: «He hecho todo lo posible para provocar el arribo del Mesías, ahora les paso a ustedes esta misión; hagan todo lo que puedan para que Él venga»[^11]. En relación al evento mesiánico, el eminente rabino Yekutiel Fish atribuyó una misión decisiva a Trump: «Todo el mundo está centrado en Gaza, pero esa es solo una parte de la agenda del fin de los tiempos, que tiene a los judíos viviendo en las fronteras profetizadas de Israel; la Torá incluye explícitamente a Gaza. [Lo que Trump está haciendo es limpiar Gaza de todos los odiadores de Israel](https://www.hiperbolajanus.com/posts/entrevista-mutti-marzo-24/). No podrán estar en Israel después de la venida del Mesías. (...) Esto incluirá a Gaza, la mitad del Líbano y gran parte de Jordania. Y vemos que casi lo hemos logrado. Siria cayó. Líbano está medio destruido. Gaza está destrozada. El escenario está casi listo para el Mesías. Pero, ¿cómo pueden los palestinos estar aquí cuando vayamos a recibir al Mesías? El Mesías necesita que alguien se ocupe de esto, y en este caso, es Donald Trump. Trump está simplemente llevando a cabo las tareas finales necesarias antes de que el Mesías sea revelado»[^12].
Esta inspiración escatológica está presente en las palabras de Pete Brian Hegseth, el pintoresco exponente del «Reconstruccionismo Cristiano»[^13] a quien Trump nombró secretario de Defensa. En un discurso pronunciado en 2019 en el Hotel Rey David de Jerusalén, con motivo de la conferencia anual del canal *Arutz Sheva* (*Israel National News*), Hegseth enalteció el «vínculo eterno» entre Israel y Estados Unidos, y enumeró los «milagros» que atestiguan el «apoyo divino» a la causa sionista, el último de los cuales será la reconstrucción del Templo judío en la zona donde actualmente se encuentra la mezquita de al-Aqsa: «La dignidad de capital adquirida por Jerusalén —dijo— fue un milagro, y no hay razón por la cual no sea posible el milagro de la restauración del Templo en el Monte del Templo».[^14]
Es conocido que el fundamentalismo evangélico pro-sionista[^15] comparte con el judaísmo la creencia en que la construcción del tercer Templo de Jerusalén marcará el comienzo de la era mesiánica; cuando la administración Trump trasladó la embajada de Estados Unidos a Jerusalén en 2017, Laurie Cardoza-Moore, exponente del evangelismo sionista, saludó así la «obediencia de Trump a la Palabra de Dios» en «Haaretz»: «Al establecer la Embajada en Jerusalén, el presidente Donald Trump está implementando una de las iniciativas históricas de dimensión bíblica en su presidencia. Al igual que muchos judíos en Israel y en todo el mundo, los cristianos reconocen el vínculo de los judíos con la Biblia a través del nombre de Jerusalén como la capital del antiguo Israel, así como el sitio del Primer y Segundo Templos. Según los profetas Ezequiel, Isaías y el apóstol Juan del Nuevo Testamento, todos los israelíes esperan la reconstrucción del Tercer Templo»[^16]. El 22 de mayo del mismo año, Donald Trump, acompañado de su esposa Melania, de su hija Ivanka y su yerno Jared Kushner, fue el primer presidente de los Estados Unidos en ejercicio en acudir al Muro de las Lamentaciones, anexionado ilegalmente a la entidad sionista.
En 2019, la administración Trump confirmó la posición de Estados Unidos al enviar en visita oficial para Jerusalén a Mike Pompeo, un secretario de Estado que —ironía de la Historia— lleva el mismo nombre del general romano que asaltó la ciudad en el año 63 a.C. «Por primera vez en la historia, un secretario de Estado norteamericano visitó la Ciudad Vieja de Jerusalén en compañía de un alto político israelí. Fue una visita histórica que reforzó las expectativas israelíes y constituyó un reconocimiento tácito de la soberanía israelí sobre el sitio del Monte del Templo y la Explanada de las Mezquitas. (…) Mike Pompeo, acompañado por el primer ministro Benjamin Netanyahu y el embajador de Estados Unidos en Israel, David Friedman, también visitó el túnel del Muro de las Lamentaciones y la sinagoga ubicada bajo tierra, en el presunto lugar del santuario del Templo[^17], donde se le mostró una maqueta del futuro Templo[^18]. En el transcurso de una entrevista concedida durante la fiesta del Purim (que celebra el exterminio de la clase política persa, ocurrido hace 2500 años), el secretario de Estado insinuó que «el presidente Donald Trump puede haber sido enviado por Dios para salvar al pueblo judío y que confiaba en que aquí el Señor estaba obrando»[^19].
Como observa Daniele Perra, en este mismo número de «Eurasia», el «mito movilizador» del Tercer Templo, atribuible a los «mitos teológicos» señalados por Roger Garaudy como mitos fundadores de la entidad sionista, «atribuye al judaísmo una especie de función sociológica de transmisión y proyección del conflicto palestino-israelí hacia el resto del mundo y confiere una inspiración apocalíptica al momento geopolítico actual».
|**Info**||
|:-|:-|
|**Autor**| Claudio Mutti |
|**Fuente**| [_I "Figli della Luce" alla Casa Bianca_](https://www.eurasia-rivista.com/i-figli-della-luce-alla-casa-bianca/) |
|**Fecha**| 8/Mar/2025 |
|**Traducción**| Francisco de la Torre |
[^1]: https://en.wikipedia.org/wiki/Prosperity_theology.
[^2]: The White House, *President Trump announces appointments to the White House Faith Office* [https://www.whitehouse.gov](https://www.whitehouse.gov/),, 7 de febrero de 2025; *Trump establece la Oficina de la Fe con una foto de «La Última Cena» | Fue dirigida por la controvertida predicadora Paula White*, [https://www.tgcom24.mediaset.it](https://www.tgcom24.mediaset.it/), 10 de febrero de 2025\.
[^3]: «We extend our heartfelt gratitude for bringing faith to the forefront of American and global culture through the establishment of the Faith Office in the White House. Your recognition of the importance of religion in public life is a step toward restoring moral values and spiritual leadership in the world» (*Letter from the Nascent Sanhedrin to President Donald J. Trump*, Jerusalem, Wednesday, February 12, 2025).
[^4]: *Israeli group mints Trump coin to honor Jerusalem recognition*, «The Times of Israel», [https://www.timesofisrael.com](https://www.timesofisrael.com/), 28-2-2018.
[^5]: Mons. Viganò — Siamo nella battaglia tra figli della luce e figli delle tenebre, https://www.italiador.com, 7-6-2020
[^6]: *TRANSCRIPT: Steve Bannon’s ‘War Room’ interview with Abp. Viganò*, lifesitenews.com, 4-1-2021. Sulle origini e sulla fortuna di questo tema cfr. C. Mutti, *Le sètte dell’Occidente*, «Eurasia», 2/2021, pp. 12-15. (https://www.eurasia-rivista.com/las-sectas-de-occidente/)
[^7]: Luke Tress, *The who’s who of Jews in Trump’s inner circle?*, «The Jerusalem Post», https://www.jpost.com, 19-11-2024.
[^8]: *Radio Talk Show Host Mark Levin Calls President Trump «the First Jewish President of the United States»*, [https://www.c-span.org](https://www.c-span.org/), 11-12-2019.
[^9]: «However, he had a change of heart and officially converted in early 2017\. The ceremony was held in private, and closely guarded for nearly two years» (*Donald Trump converted to Judaism two years ago, according to White House official*, https://israeltodaynews.blogspot.com/2019/02).
[^10]: «El rabino Kirt Schneider (...) es un millonario judío, una figura televisiva de los “judíos mesiánicos”. Sus emisiones televisivas semanales son emitidas por más de treinta canales cristianos en unos doscientos países; entre ellos, los canales “Yes” y “Hot” en Israel. Solo en Estados Unidos, sus emisiones atraen a 1.600.000 telespectadores cada semana. Kirt Schneider dirige un imperio de telecomunicaciones que tiene un millón y medio de seguidores en Facebook, X (antes Twitter) y YouTube» (Pierre-Antoine Plaquevent — Youssef Hindi, *El milenarismo teopolítico de Israel*, Edizioni all'insegna del Veltro, Parma 2025, p. 31).
[^11]: https://it.wikipedia.org/wiki/Menachem_Mendel_Schneerson
[^12]: «Everyone is focused on Gaza, but that is only one part of the end-of-days agenda, which has the Jews living in Israel’s prophesied borders. The Torah explicitly includes Gaza. What Trump is doing is cleaning out Gaza of all the haters of Israel. They cannot be in Israel after the Messiah comes. (…) This will include Gaza, half of Lebanon, and much of Jordan. And we see that we are almost there. Syria fell. Lebanon is half gone. Gaza is ripped up. The stage is nearly set for Messiah. But how can the Palestinians be here when we go to greet the Messiah? The Messiah needs someone to take care of this, and in this case, it is Donald Trump. Trump is merely carrying out the final tasks needed before Messiah is revealed» (Adam Eliyahu Berkowitz, *Trump’s Gaza Plan is «The Final task before Messiah»*, [https://israel365news.com](https://israel365news.com/), 5-2-2025).
[^13]: «A day after Hegseth was announced for the Cabinet position, Brooks Potteiger, a pastor within the Communion of Reformed Evangelical Churches (CREC), posted on X that Hegseth is a member of the church in good standing. The CREC, a denomination of Christian Reconstructionism, is considered by some academics to be an extremist, Christian supremacist movement» (Shannon Bond e altri, *What’s behind defense secretary pick Hegseth’s war on ‘woke’*, [https://www.npr.org](https://www.npr.org/), 14-11-2024.
[^14]: «The decoration of Jerusalem as a capital was a miracle, and there is no reason why the miracle of the re-establishment of Temple on the Temple Mount is not possible» (*Pete Hegseth at Arutz Sheva Conference*, youtube.com). Cfr. Daniele Perra, *Paleotrumpismo, neotrumpismo e post-trumpismo*, in: AA. VV., *Trumpismo*, Cinabro Edizioni, Roma 2025, pp. 22-23.
[^15]: Pierre-Antoine Plaquevent — Youssef Hindi, *El milenarismo teopolítico de Israel*, cit., págs. 82 a 96.
[^16]: «We American Christians Welcome Trump’s Obedience to God’s Word on Jerusalem», «Haaretz», 6-12-2017.
[^17]: Pierre-Antoine Plaquevent — Youssef Hindi, *El milenarismo teopolítico de Israel*, cit., pág. 97.
[^18]: *Pompeo en visite historique au mur Occidental aux côtés de Netanyahu et Friedman*, «The Times of Israel», [https://fr.timesofisrael.com](https://fr.timesofisrael.com/), 21-3-2019.
[^19]: *Pompeo says Trump may have been sent by God to save Jews from Iran*, «The Times of Israel», 22-3-2019.
---
**Artículo original**: Claudio Mutti, [_Los «hijos de la luz» en la Casa Blanca_](https://www.hiperbolajanus.com/posts/hijos-luz-casa-blanca/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/hijos-luz-casa-blanca/), 25/Mar/2025
-

@ 91bea5cd:1df4451c
2025-02-04 17:24:50
### Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits
Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C.
e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
#### Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid()
RETURNS TEXT
AS $$
DECLARE
-- Crockford's Base32
encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ';
timestamp BYTEA = E'\\000\\000\\000\\000\\000\\000';
output TEXT = '';
unix_time BIGINT;
ulid BYTEA;
BEGIN
-- 6 timestamp bytes
unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT;
timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes
ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output;
END
$$
LANGUAGE plpgsql
VOLATILE;
```
#### ULID TO UUID
```sql
CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$
DECLARE
-- 16byte
bytes bytea = E'\\x00000000 00000000 00000000 00000000';
v char[];
-- Allow for O(1) lookup of index values
dec integer[] = ARRAY[
255, 255, 255, 255, 255, 255, 255, 255, 255, 255,
255, 255, 255, 255, 255, 255, 255, 255, 255, 255,
255, 255, 255, 255, 255, 255, 255, 255, 255, 255,
255, 255, 255, 255, 255, 255, 255, 255, 255, 255,
255, 255, 255, 255, 255, 255, 255, 0, 1, 2,
3, 4, 5, 6, 7, 8, 9, 255, 255, 255,
255, 255, 255, 255, 10, 11, 12, 13, 14, 15,
16, 17, 1, 18, 19, 1, 20, 21, 0, 22,
23, 24, 25, 26, 255, 27, 28, 29, 30, 31,
255, 255, 255, 255, 255, 255, 10, 11, 12, 13,
14, 15, 16, 17, 1, 18, 19, 1, 20, 21,
0, 22, 23, 24, 25, 26, 255, 27, 28, 29,
30, 31
];
BEGIN
IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN
RAISE EXCEPTION 'Invalid ULID: %', ulid;
END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits)
bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]);
bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2));
bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4));
bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1));
bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3));
bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits);
bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2));
bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4));
bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1));
bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3));
bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]);
bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2));
bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4));
bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1));
bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3));
bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes;
END
$$
LANGUAGE plpgsql
IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$
BEGIN
RETURN encode(parse_ulid(ulid), 'hex')::uuid;
END
$$
LANGUAGE plpgsql
IMMUTABLE;
```
#### UUID to ULID
```sql
CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$
DECLARE
encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ';
output text = '';
uuid_bytes bytea = uuid_send(id);
BEGIN
-- Encode the timestamp
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output;
END
$$
LANGUAGE plpgsql
IMMUTABLE;
```
#### Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql
-- Cria a extensão pgcrypto para gerar uuid
CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID
CREATE OR REPLACE FUNCTION gen_lrandom()
RETURNS TEXT AS $$
DECLARE
ts_millis BIGINT;
ts_chars TEXT;
random_bytes BYTEA;
random_chars TEXT;
base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ';
i INT;
BEGIN
-- Pega o timestamp em milissegundos
ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32
ts_chars := '';
FOR i IN REVERSE 0..11 LOOP
ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1);
END LOOP;
-- Gera 10 bytes aleatórios e converte para base32
random_bytes := gen_random_bytes(10);
random_chars := '';
FOR i IN 0..9 LOOP
random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1);
IF i < 9 THEN
random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1);
ELSE
random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1);
END IF;
END LOOP;
-- Concatena o timestamp e os caracteres aleatórios
RETURN ts_chars || random_chars;
END;
$$ LANGUAGE plpgsql;
```
#### Exemplo de USO
```sql
-- Criação da extensão caso não exista
CREATE EXTENSION
IF
NOT EXISTS pgcrypto;
-- Criação da tabela pessoas
CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela
SELECT
*
FROM
"pessoas"
WHERE
uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F';
```
### Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-

@ bcbb3e40:a494e501
2025-03-31 15:34:12
|[](https://www.hiperbolajanus.com/libros/thiriart-joven-europa-missiaggia/)|
|:-:|
|[MISSIAGGIA, Pietro; _Jean Thiriart, el caballero euroasiático y la Joven Europa_; Hipérbola Janus, 2025](https://www.hiperbolajanus.com/libros/thiriart-joven-europa-missiaggia/)|
Desde nuestros inicios los autores y temáticas relacionadas con la geopolítica nos han procurado atención e interés por parte del gran público y de los *mass media*, y no hay más que recordar el efecto que han venido teniendo nuestras obras de [**Aleksandr Duguin**](https://hiperbolajanus.com/firmas/aleksandr-g.-duguin/), en especial [*La geopolítica de Rusia*](https://hiperbolajanus.com/libros/geopolitica-rusia-aleksandr-duguin/) y [*Proyecto Eurasia: teoría y praxis*](https://hiperbolajanus.com/libros/proyecto-eurasia-aleksandr-duguin/), sobre todo a raíz de [nuestra presentación en Casa de Rusia](https://youtu.be/rsp-FMmSPJE) en un ya lejano 2016, con la inestimable colaboración de [**Jordi de la Fuente**](https://hiperbolajanus.com/firmas/jordi-de-la-fuente-miro/) como prologuista, trabajo que siempre reivindicamos desde nuestros medios por el prestigio, la calidad y brillantez de exposición del mismo.
Más allá de las obras del prestigioso y afamado filósofo y politólogo ruso, también hemos realizado otras incursiones en esta vertiente, que podríamos llamar «geopolítica alternativa», introduciendo las obras de otros notables autores como [**Claudio Mutti**](https://amzn.to/3RfXOUZ), [**Carlo Terracciano**](https://amzn.to/4iq9mkA) o [**Boris Nad**](https://amzn.to/3Fv98tT). Con estos autores hemos tratado de profundizar en esa vía que se opone frontalmente, y radicalmente si se quiere, a los planteamientos derivados de la geopolítica atlantista y liberal que tiene su principal polo en Estados Unidos, haciendo especial hincapié en el subyugamiento que vienen ejerciendo desde 1945 en adelante respecto a una Europa convertida en un protectorado en una mera colonia.
Es por este motivo por el que la publicación de _Jean Thiriart, el caballero euroasiático y la Joven Europa_ nos parece una obra totalmente pertinente en estos momentos, forma parte del desarrollo lógico de la línea editorial en la que estamos encauzados desde nuestros inicios, y viene a representar una de las múltiples vías en las que confluye la idea, [profundamente schmittiana](https://hiperbolajanus.com/posts/tierra-mar-katechon/), de la política de los grandes espacios. En este caso la idea de una Europa unida, bajo un vasto proyecto que traspasa los estrechos límites del continente concebido como un apéndice más del [«Occidente», de ese subproducto ideológico decadente y funcional a los intereses del otro lado del Atlántico](https://hiperbolajanus.com/posts/presentacion-despues-virus-boris-nad/). Para comprender la idea de una Europa unida, que comprenda a Rusia, y su enorme extensión territorial a lo largo de 17 millones de kilómetros cuadrados, y la importancia estratégica de su ubicación, es necesario recurrir al legado de **Jean Thiriart**, conocer su obra, pero también al hombre, pues una no se comprende sin el otro, en este caso hablamos de elementos correlativos.
||
|:-:|
|Jean Thiriart (1922-1992)|
¿Pero quién fue Jean Thiriart? Esta obra nos permite adentrarnos en aspectos biográficos, algunos de ellos poco conocidos para el gran público de habla hispana, y saber de su trayectoria, de la maduración de sus ideas, de su proyecto político y de las etapas que componen el desarrollo del mismo y que aparecen claramente diferenciadas: hablamos del proyecto político de unidad europea, que alcanza su concreción teórica en *¡Arriba Europa!: Una Europa unida: un imperio de 400 millones de hombres* (1965, Editorial Mateu, Barcelona), en pleno apogeo de la organización *Jeune Europe*, que se convirtió en el órgano político a partir del cual creyó poder implementar su proyecto unitario a escala europeo, manteniendo una posición de independencia respecto a los dos pretendidos bloques antagónicos de Guerra Fría: Estados Unidos y la Unión Soviética. En esa época, estamos hablando del ecuador de los años 60, [todo el mundo de la Contracultura](https://hiperbolajanus.com/posts/mito-contracultura/), falsamente contestatario, estaba articulando su propio discurso, que tendría su expresión más nítida a través del ya conocido Mayo del 68 francés o la Primavera de Praga, durante el mismo año. Y si el movimiento de Nueva Derecha liderado por **Alain de Benoist** surgiría en lo sucesivo, ya en la década de los años 70, como una «reacción» frente a la «rebelión contracultural», no podemos obviar la importancia de un movimiento político como *Jeune Europe*, una organización política transnacional, a escala de la Europa occidental, con sus diferentes delegaciones en países como Francia, Italia, Alemania, la propia España además de, como es obvio, Bélgica, país de origen de nuestro autor.
Jean Thiriart ha sido etiquetado con reiteración como un político y teórico de «extrema derecha», se han hecho numerosos discursos interesados para vincularlo, por cuestiones de orden biográfico muy circunscritas a determinado periodo, con el fascismo y el nacionalsocialismo de entreguerras. Sin embargo, y como el lector podrá descubrir a lo largo de la presente obra, el pensamiento de nuestro autor está muy lejos de ser reducible a meras etiquetas, y en ningún caso mostró las filiaciones que se le atribuyen desde posicionamientos ideológicos, sino que, muy al contrario, vemos a un hombre de pensamiento racional y pragmático, poderosamente influenciado por la geopolítica y abierto a alianzas estratégicas más variadas, más allá de todo fundamentalismo ideológico. Es por este motivo que veremos a un Thiriart buscando sinergias y entendimiento entre círculos de izquierdas, antiimperialistas en una lucha concebida como «cuatricontinental». No en vano, muchos de los cuadros políticos que se formaron en *Giovane Europa*, la rama italiana, terminaron por militar incluso en organizaciones de extrema izquierda de inspiración maoísta. En el caso de España hubo un notable apoyo a la organización por parte de los falangistas más disidentes. De manera que Jean Thiriart representa una figura política compleja, con influencias variadas, que van desde los hermanos **Strasser**, pasando por **Ernst Niekish** o **Vilfredo Pareto**, e incluso, por **Sieyès** o **Robespierre**.
Es a partir de *Jeune Europe* cuando el nacionalismo europeo, la idea de una Europa unida desde Brest a Bucarest toma cuerpo. En la obra mencionada con anterioridad (*¡Arriba Europa!: Una Europa unida: un imperio de 400 millones de hombres*) Jean Thiriart ya nos presenta a través de unos trazos muy definidos el proyecto del comunitarismo nacional-europeo, la piedra angular de su proyecto político. La idea de un socialismo aristocrático y europeo, trascendiendo las fronteras del Estado-nación liberal decimonónico, y los particularismos nacionales, concebidos como formas obsoletas y «estrechas de miras», obstáculos a superar en la convergencia del Imperio europeo. Porque vemos a un Thiriart que potencia la estructura del Estado, del aparato de poder, tratando de potenciar, y restaurar naturalmente, el papel y la preponderancia de Europa como espacio de civilización en el mundo. Es un nacionalismo europeo que viene determinado por razones puramente geopolíticas, algo que también fue objeto de críticas, concretamente por parte del geopolítico austriaco **Heinrich von Lohausen**, y que también recogemos en el presente volúmen de la obra.
||
|:-:|
|Ejemplar de una de las publicaciones más importantes de Joven Europa (Jeune Europe) cuya portada refleja el antiamericanismo y antiimperialismo característicos del nacionalismo europeo de la organización.|
En este sentido, Thiriart no andaba nada desencaminado, en la medida que pensaba que solo los Estados de dimensiones continentales podrían ser capaces de defender su independencia y soberanía, y ejercer un poder en el mundo, frente a los antiguos nacionalismos europeos, totalmente anacrónicos y un factor de ruptura y desintegración del potencial europeo. En este contexto, se hace necesario eliminar el orden establecido en Yalta en 1945, que convierte a Europa en un vasallo de las grandes potencias vencedoras de la Segunda Guerra Mundial. De modo que luchar contra la ocupación estadounidense por un lado, y soviética por otro lado, fuese el principal *leitmotiv* del Partido Revolucionario Europeo, un partido histórico señala Thiriart, encargado de llevar a término la acción unificadora continental. Y es con este propósito con el que se tratan de concertar una serie de alianzas internacionales que llevó a Thiriart y su organización a tratar con personal diplomático y gubernamental de los países árabes no alineados, del régimen de **Fidel Castro** o incluso con emisarios del gobierno chino, como ocurrió en el famoso encuentro propiciado por **Ceaucescu** en Bucarest con **Zhou En-Lai**.
Quizás, uno de los puntos donde más desacuerdos encontramos con las teorías thiriartianas se encuentra en ciertos fundamentos que la articulan, en un modelo racionalista, materialista y pragmático, de hecho no debemos olvidar que **Maquiavelo** era uno de sus referentes, y con éste la posterior hornada de autores neomaquiavélicos como Vilfredo Pareto. El excesivo pragmatismo de sus planteamientos, un estatalismo exacerbado y sin concesiones a las particularidades de los pueblos, una suerte de centralismo jacobino, y la ausencia de un elemento trascendente capaz de dar una justificación metafísica a todo el proyecto nacional europeo constituyen, en nuestra opinión, una parte discutible y reformulable.
En otro terreno, como pueda ser el puramente económico, encontramos un proyecto anticapitalista en muchos de sus aspectos, frente al democratismo parlamentario liberal, y apoyándose en las teorías económicas de **Johann G. Fichte** o **Friedrich List**, rechazando cualquier organización económica transnacional que pueda mediatizar o convertir a Europa en objeto de sus actividades usurocráticas y depredatorias, colocando la soberanía e independencia económica europea en una de las máximas prioridades en este terreno.
Debemos destacar, porque es un elemento de debate especialmente interesante, el apartado del libro que se corresponde al escrito de **Luc Michel**, publicado en Italia bajo el título *Da Jeune Europe alle Brigate Rosse*, en el libro *Parte II Historia de Jeune Europe (1962-1969)*, en el que se detallan las colaboraciones que comenzaron a sucederse entre la militancia de la delegación italiana, *Giovane Europa*, y círculos de extrema izquierda maoísta, y cómo muchos de los antiguos militantes nacional-europeos terminaron militando en organizaciones de esta facción ideológica, y nos referimos a casos tan representativos en la época como **Claudio Orsoni** o **Pino Bolzano** entre otros muchos.
La actividad proselitista de *Jeune Europe* en el último lustro de la década de los años 60, con la fundación del Partido Comunitario Europeo, nos legó una gran cantidad de publicaciones, entre las cuales destacaron *La Nation Européenne*, *La Nazione Europea* o *Europa Combattente*, cuyas portadas han servido para ilustrar las páginas interiores de nuestra obra, y que procuraron una actividad proselitista y de difusión de ideas que llegaron a imprimir semanal y mensualmente varios miles de ejemplares en Francia o en Italia.
Tras agotar todas las vías posibles de alianzas y convergencias, con encuentros poco afortunados, vemos a un Thiriart que prefiere adoptar otras vías para seguir construyendo el proyecto nacional-europeo más allá de la fórmula activista y del partido político. Este es el motivo por el cual, en los siguientes años, ya en la última etapa de su vida, veremos esa transición del político activista al teórico y al ideólogo como parte de una nueva estrategia dentro del proyecto político al que consagró buena parte de su vida, y es un hecho que comienza a apreciarse desde mediados de los años 70. Durante esta época la «Europa de Brest a Bucarest» se transforma y amplía en una «Europa desde Dublín a Vladivostok». Thiriart aborda ya abiertamente la integración del espacio soviético en una Europa unida que abarca un inmenso espacio territorial, capaz de unir el Océano Atlántico y el Océano Pacífico de un extremo a otro, el «Imperio Eurosoviético». No obstante, Thiriart siempre piensa en términos geopolíticos, y considera que este proceso de integración debe llevarse a cabo desde una revisión de la ideología soviética, desde una marcada desmarxistización de su socialismo, purgado de todo dogmatismo y elementos condicionantes derivados de la teoría del Estado formulada por el marxismo-leninismo para tomar en su lugar aquella de **Thomas Hobbes**.
A partir de este momento solamente hay un enemigo, el que representa el poder estadounidense y el dominio que éste ejerce sobre la Europa occidental. A partir de ese momento la URSS, bajo las premisas apuntadas por Thiriart, y desde una ideología soviética «desmarxistizada», es la que debe asumir el proyecto de integración europea. Todo este enfoque terminará conociendo su colofón final al final de la vida de Jean Thiriart, cuando éste se encuentre ya en sus último año de vida, en 1992, con una Unión Soviética ya periclitada y disuelta, con un país sumido en una crisis económica, política y social bajo el gobierno decadente de **Yeltsin**, con un poder notablemente menguado y a merced de las potencias extranjeras y las apetencias de las organizaciones financieras transnacionales. En este contexto tendrá lugar el conocido viaje de Jean Thiriart a Moscú, donde se encontrará, además de con la disidencia de Yeltsin, encabezada por el Partido Comunista dirigido por **Gennadij Ziuganov** y numerosas personalidades públicas del ámbito ruso, entre las que destacará por encima de todos el filósofo y politólogo **Aleksandr Duguin**, quien en la presente obra también reivindica la figura del belga como un contribuidor directo del [pensamiento euroasiático](https://amzn.to/3FsF3Lr). Además de medios de prensa, políticos e intelectuales rusos, nuestro autor también compartirá espacio con una pequeña delegación de la revista italiana «Orion», especializada en temática geopolítica, y representada por el padre de la geopolítica italiana, Carlo Terracciano. El encuentro no tendrá mayores consecuencias, y vendrá a significar el último acto de servicio de Jean Thiriart en su denodado esfuerzo por lograr la integración de Europa y Rusia en un poderoso bloque geopolítico capaz de hacer frente a la hegemonía estadounidense en el mundo.
Terminaremos este breve y sintético escrito de presentación con un fragmento de la obra que Jean Thiriart publicó en 1965 bajo el título *¡Arriba Europa!: Una Europa unida: un imperio de 400 millones de hombres*, que nos parece de lo más adecuado para poner el punto final al presente texto:
> Europa, este **MILAGRO** en la historia del hombre, este milagro que siguió al milagro griego, ha dado vida, con la prodigiosa fecundidad de su civilización irrepetible, a una cultura adoptada por el mundo entero. En la competencia surgida entre las grandes civilizaciones —occidental, india, china y japonesa— la nuestra ha aplastado a las demás.
>
> La **civilización** es creadora de cultura. La cultura, en cambio, jamás ha creado civilización.
>
> **SOLO** Europa posee la civilización; de ahí deriva su supremacía sobre los Estados Unidos y la Rusia comunista, que poseen únicamente la cultura nacida de nuestra civilización, como ha demostrado magistralmente Oswald Spengler.
>
> Esta cultura, separada de su civilización, está condenada a la esterilidad, la cual se manifestará primero mediante una esclerosis y, posteriormente, mediante un retorno a la barbarie.
>
> Políticamente dominada por Moscú o por Washington, la civilización europea se ve asfixiada y corre el riesgo de estancarse en su estado de simple cultura. Basta notar que todos los descubrimientos en el campo nuclear y astronáutico son obra de europeos. Todos buscan a los científicos europeos.
>
> Solo una Europa políticamente unida puede proveer los medios de poder que garantizarán las condiciones históricas indispensables para la supervivencia de esta civilización.
>
> Ninguna otra potencia, por otra parte, podría sustituir a Europa en su misión hacia la humanidad.
---
**Artículo original**: Hipérbola Janus, [_Presentación de «Jean Thiriart, el caballero euroasiático y la Joven Europa», de Pietro Missiaggia_](https://www.hiperbolajanus.com/posts/presentacion-thiriart-missiaggia/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/presentacion-thiriart-missiaggia/), 18/Mar/2025
-

@ 91bea5cd:1df4451c
2025-02-04 17:15:57
### Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits
Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C.
e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
#### Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid()
RETURNS TEXT
AS $$
DECLARE
-- Crockford's Base32
encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ';
timestamp BYTEA = E'\\000\\000\\000\\000\\000\\000';
output TEXT = '';
unix_time BIGINT;
ulid BYTEA;
BEGIN
-- 6 timestamp bytes
unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT;
timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes
ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output;
END
$$
LANGUAGE plpgsql
VOLATILE;
```
#### ULID TO UUID
```sql
CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$
DECLARE
-- 16byte
bytes bytea = E'\\x00000000 00000000 00000000 00000000';
v char[];
-- Allow for O(1) lookup of index values
dec integer[] = ARRAY[
255, 255, 255, 255, 255, 255, 255, 255, 255, 255,
255, 255, 255, 255, 255, 255, 255, 255, 255, 255,
255, 255, 255, 255, 255, 255, 255, 255, 255, 255,
255, 255, 255, 255, 255, 255, 255, 255, 255, 255,
255, 255, 255, 255, 255, 255, 255, 0, 1, 2,
3, 4, 5, 6, 7, 8, 9, 255, 255, 255,
255, 255, 255, 255, 10, 11, 12, 13, 14, 15,
16, 17, 1, 18, 19, 1, 20, 21, 0, 22,
23, 24, 25, 26, 255, 27, 28, 29, 30, 31,
255, 255, 255, 255, 255, 255, 10, 11, 12, 13,
14, 15, 16, 17, 1, 18, 19, 1, 20, 21,
0, 22, 23, 24, 25, 26, 255, 27, 28, 29,
30, 31
];
BEGIN
IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN
RAISE EXCEPTION 'Invalid ULID: %', ulid;
END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits)
bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]);
bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2));
bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4));
bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1));
bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3));
bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits);
bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2));
bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4));
bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1));
bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3));
bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]);
bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2));
bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4));
bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1));
bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3));
bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes;
END
$$
LANGUAGE plpgsql
IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$
BEGIN
RETURN encode(parse_ulid(ulid), 'hex')::uuid;
END
$$
LANGUAGE plpgsql
IMMUTABLE;
```
#### UUID to ULID
```sql
CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$
DECLARE
encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ';
output text = '';
uuid_bytes bytea = uuid_send(id);
BEGIN
-- Encode the timestamp
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output;
END
$$
LANGUAGE plpgsql
IMMUTABLE;
```
#### Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql
-- Cria a extensão pgcrypto para gerar uuid
CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID
CREATE OR REPLACE FUNCTION gen_lrandom()
RETURNS TEXT AS $$
DECLARE
ts_millis BIGINT;
ts_chars TEXT;
random_bytes BYTEA;
random_chars TEXT;
base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ';
i INT;
BEGIN
-- Pega o timestamp em milissegundos
ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32
ts_chars := '';
FOR i IN REVERSE 0..11 LOOP
ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1);
END LOOP;
-- Gera 10 bytes aleatórios e converte para base32
random_bytes := gen_random_bytes(10);
random_chars := '';
FOR i IN 0..9 LOOP
random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1);
IF i < 9 THEN
random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1);
ELSE
random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1);
END IF;
END LOOP;
-- Concatena o timestamp e os caracteres aleatórios
RETURN ts_chars || random_chars;
END;
$$ LANGUAGE plpgsql;
```
#### Exemplo de USO
```sql
-- Criação da extensão caso não exista
CREATE EXTENSION
IF
NOT EXISTS pgcrypto;
-- Criação da tabela pessoas
CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela
SELECT
*
FROM
"pessoas"
WHERE
uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F';
```
### Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-

@ e3ba5e1a:5e433365
2025-02-04 08:29:00
President Trump has started rolling out his tariffs, something I [blogged about in November](https://www.snoyman.com/blog/2024/11/steelmanning-tariffs/). People are talking about these tariffs a lot right now, with many people (correctly) commenting on how consumers will end up with higher prices as a result of these tariffs. While that part is true, I’ve seen a lot of people taking it to the next, incorrect step: that consumers will pay the entirety of the tax. I [put up a poll on X](https://x.com/snoyberg/status/1886035800019599808) to see what people thought, and while the right answer got a lot of votes, it wasn't the winner.

For purposes of this blog post, our ultimate question will be the following:
* Suppose apples currently sell for $1 each in the entire United States.
* There are domestic sellers and foreign sellers of apples, all receiving the same price.
* There are no taxes or tariffs on the purchase of apples.
* The question is: if the US federal government puts a $0.50 import tariff per apple, what will be the change in the following:
* Number of apples bought in the US
* Price paid by buyers for apples in the US
* Post-tax price received by domestic apple producers
* Post-tax price received by foreign apple producers
Before we can answer that question, we need to ask an easier, first question: before instituting the tariff, why do apples cost $1?
And finally, before we dive into the details, let me provide you with the answers to the ultimate question. I recommend you try to guess these answers before reading this, and if you get it wrong, try to understand why:
1. The number of apples bought will go down
2. The buyers will pay more for each apple they buy, but not the full amount of the tariff
3. Domestic apple sellers will receive a *higher* price per apple
4. Foreign apple sellers will receive a *lower* price per apple, but not lowered by the full amount of the tariff
In other words, regardless of who sends the payment to the government, both taxed parties (domestic buyers and foreign sellers) will absorb some of the costs of the tariff, while domestic sellers will benefit from the protectionism provided by tariffs and be able to sell at a higher price per unit.
## Marginal benefit
All of the numbers discussed below are part of a [helper Google Sheet](https://docs.google.com/spreadsheets/d/14ZbkWpw1B9Q1UDB9Yh47DmdKQfIafVVBKbDUsSIfGZw/edit?usp=sharing) I put together for this analysis. Also, apologies about the jagged lines in the charts below, I hadn’t realized before starting on this that there are [some difficulties with creating supply and demand charts in Google Sheets](https://superuser.com/questions/1359731/how-to-create-a-supply-demand-style-chart).
Let’s say I absolutely love apples, they’re my favorite food. How much would I be willing to pay for a single apple? You might say “$1, that’s the price in the supermarket,” and in many ways you’d be right. If I walk into supermarket A, see apples on sale for $50, and know that I can buy them at supermarket B for $1, I’ll almost certainly leave A and go buy at B.
But that’s not what I mean. What I mean is: how high would the price of apples have to go *everywhere* so that I’d no longer be willing to buy a single apple? This is a purely personal, subjective opinion. It’s impacted by how much money I have available, other expenses I need to cover, and how much I like apples. But let’s say the number is $5.
How much would I be willing to pay for another apple? Maybe another $5. But how much am I willing to pay for the 1,000th apple? 10,000th? At some point, I’ll get sick of apples, or run out of space to keep the apples, or not be able to eat, cook, and otherwise preserve all those apples before they rot.
The point being: I’ll be progressively willing to spend less and less money for each apple. This form of analysis is called *marginal benefit*: how much benefit (expressed as dollars I’m willing to spend) will I receive from each apple? This is a downward sloping function: for each additional apple I buy (quantity demanded), the price I’m willing to pay goes down. This is what gives my personal *demand curve*. And if we aggregate demand curves across all market participants (meaning: everyone interested in buying apples), we end up with something like this:
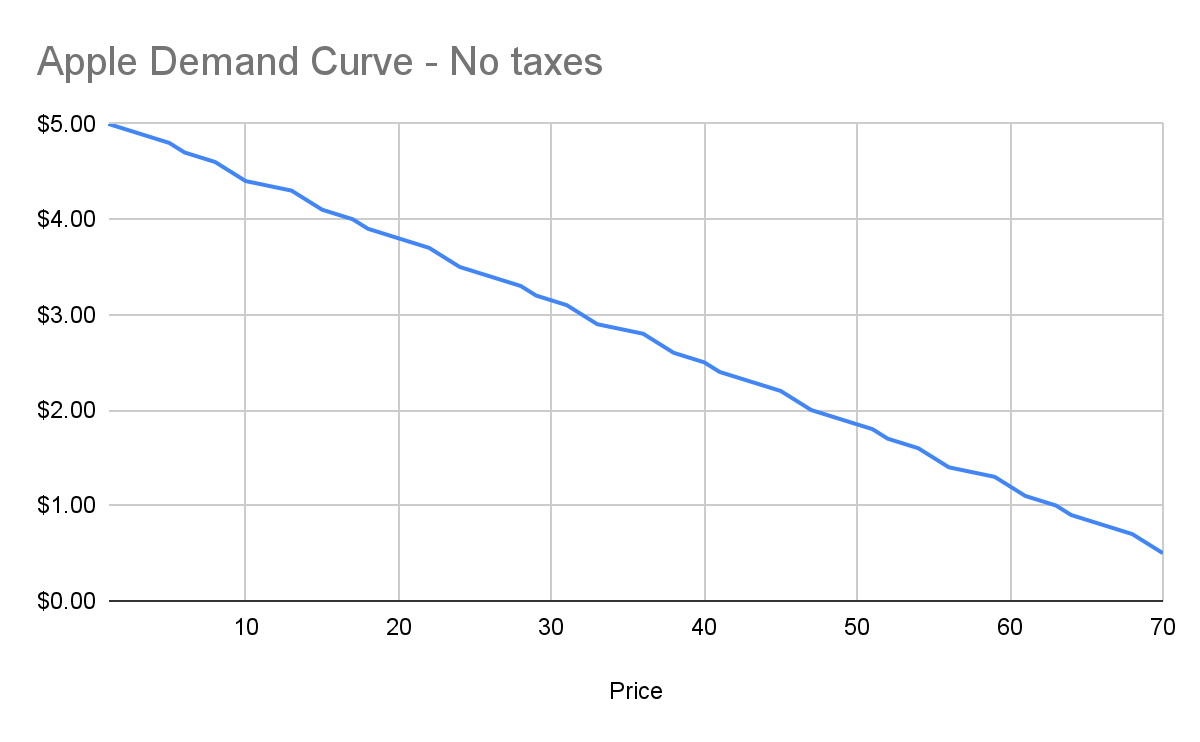
Assuming no changes in people’s behavior and other conditions in the market, this chart tells us how many apples will be purchased by our buyers at each price point between $0.50 and $5. And ceteris paribus (all else being equal), this will continue to be the demand curve for apples.
## Marginal cost
Demand is half the story of economics. The other half is supply, or: how many apples will I sell at each price point? Supply curves are upward sloping: the higher the price, the more a person or company is willing and able to sell a product.
Let’s understand why. Suppose I have an apple orchard. It’s a large property right next to my house. With about 2 minutes of effort, I can walk out of my house, find the nearest tree, pick 5 apples off the tree, and call it a day. 5 apples for 2 minutes of effort is pretty good, right?
Yes, there was all the effort necessary to buy the land, and plant the trees, and water them… and a bunch more than I likely can’t even guess at. We’re going to ignore all of that for our analysis, because for short-term supply-and-demand movement, we can ignore these kinds of *sunk costs*. One other simplification: in reality, supply curves often start descending before ascending. This accounts for achieving efficiencies of scale after the first number of units purchased. But since both these topics are unneeded for understanding taxes, I won’t go any further.
Anyway, back to my apple orchard. If someone offers me $0.50 per apple, I can do 2 minutes of effort and get $2.50 in revenue, which equates to a $75/hour wage for me. I’m more than happy to pick apples at that price\!
However, let’s say someone comes to buy 10,000 apples from me instead. I no longer just walk out to my nearest tree. I’m going to need to get in my truck, drive around, spend the day in the sun, pay for gas, take a day off of my day job (let’s say it pays me $70/hour). The costs go up significantly. Let’s say it takes 5 days to harvest all those apples myself, it costs me $100 in fuel and other expenses, and I lose out on my $70/hour job for 5 days. We end up with:
* Total expenditure: $100 \+ $70 \* 8 hours a day \* 5 days \== $2900
* Total revenue: $5000 (10,000 apples at $0.50 each)
* Total profit: $2100
So I’m still willing to sell the apples at this price, but it’s not as attractive as before. And as the number of apples purchased goes up, my costs keep increasing. I’ll need to spend more money on fuel to travel more of my property. At some point I won’t be able to do the work myself anymore, so I’ll need to pay others to work on the farm, and they’ll be slower at picking apples than me (less familiar with the property, less direct motivation, etc.). The point being: at some point, the number of apples can go high enough that the $0.50 price point no longer makes me any money.
This kind of analysis is called *marginal cost*. It refers to the additional amount of expenditure a seller has to spend in order to produce each additional unit of the good. Marginal costs go up as quantity sold goes up. And like demand curves, if you aggregate this data across all sellers, you get a supply curve like this:
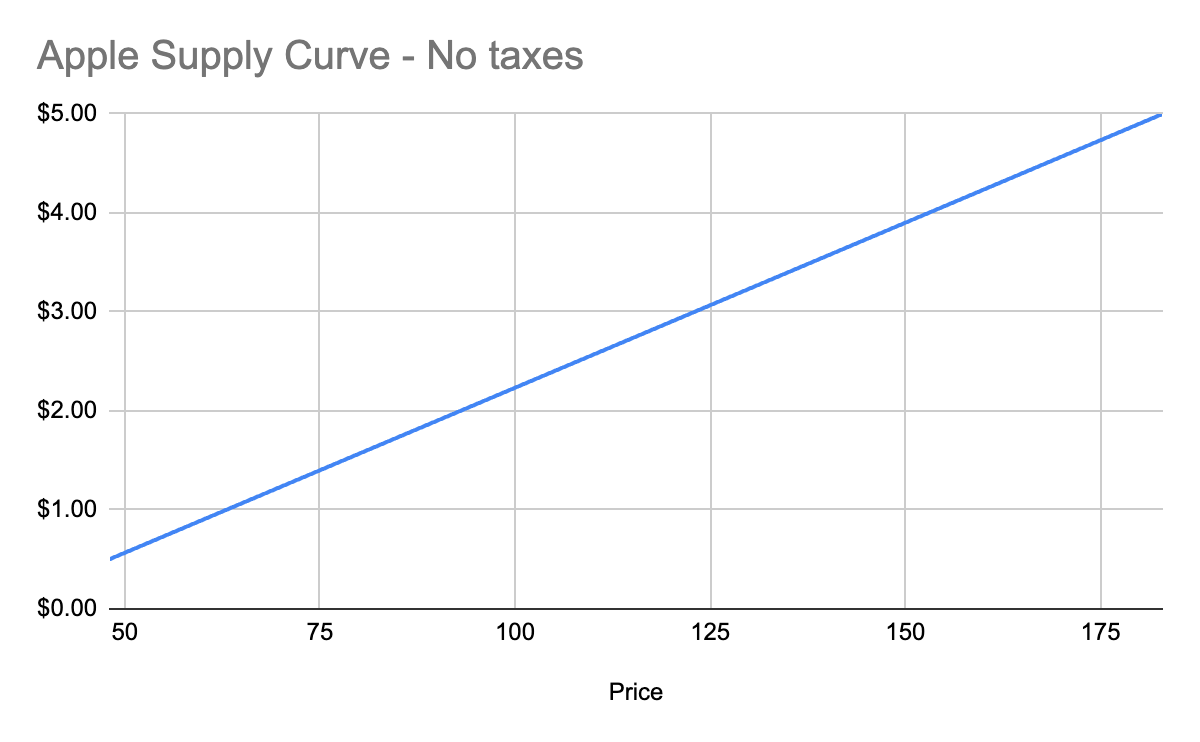
## Equilibrium price
We now know, for every price point, how many apples buyers will purchase, and how many apples sellers will sell. Now we find the equilibrium: where the supply and demand curves meet. This point represents where the marginal benefit a buyer would receive from the next buyer would be less than the cost it would take the next seller to make it. Let’s see it in a chart:
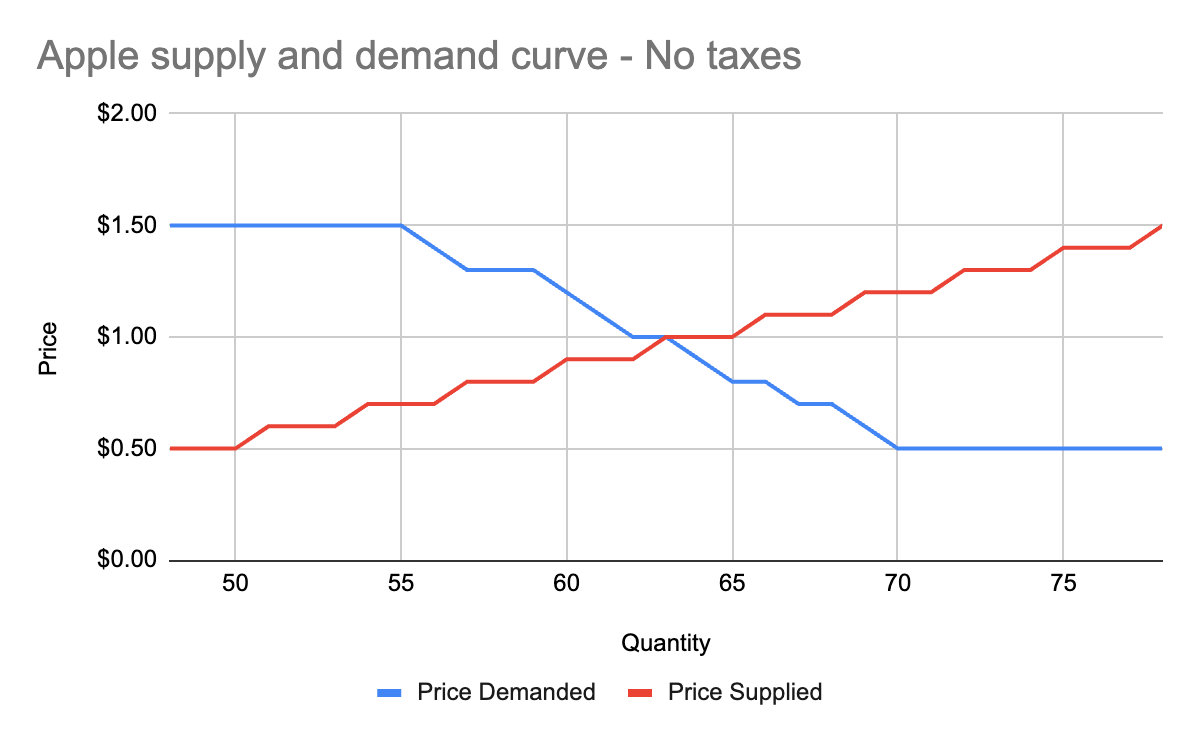
You’ll notice that these two graphs cross at the $1 price point, where 63 apples are both demanded (bought by consumers) and supplied (sold by producers). This is our equilibrium price. We also have a visualization of the *surplus* created by these trades. Everything to the left of the equilibrium point and between the supply and demand curves represents surplus: an area where someone is receiving something of more value than they give. For example:
* When I bought my first apple for $1, but I was willing to spend $5, I made $4 of consumer surplus. The consumer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and above the equilibrium price point.
* When a seller sells his first apple for $1, but it only cost $0.50 to produce it, the seller made $0.50 of producer surplus. The producer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and below the equilibrium price point.
Another way of thinking of surplus is “every time someone got a better price than they would have been willing to take.”
OK, with this in place, we now have enough information to figure out how to price in the tariff, which we’ll treat as a negative externality.
## Modeling taxes
Alright, the government has now instituted a $0.50 tariff on every apple sold within the US by a foreign producer. We can generally model taxes by either increasing the marginal cost of each unit sold (shifting the supply curve up), or by decreasing the marginal benefit of each unit bought (shifting the demand curve down). In this case, since only some of the producers will pay the tax, it makes more sense to modify the supply curve.
First, let’s see what happens to the foreign seller-only supply curve when you add in the tariff:
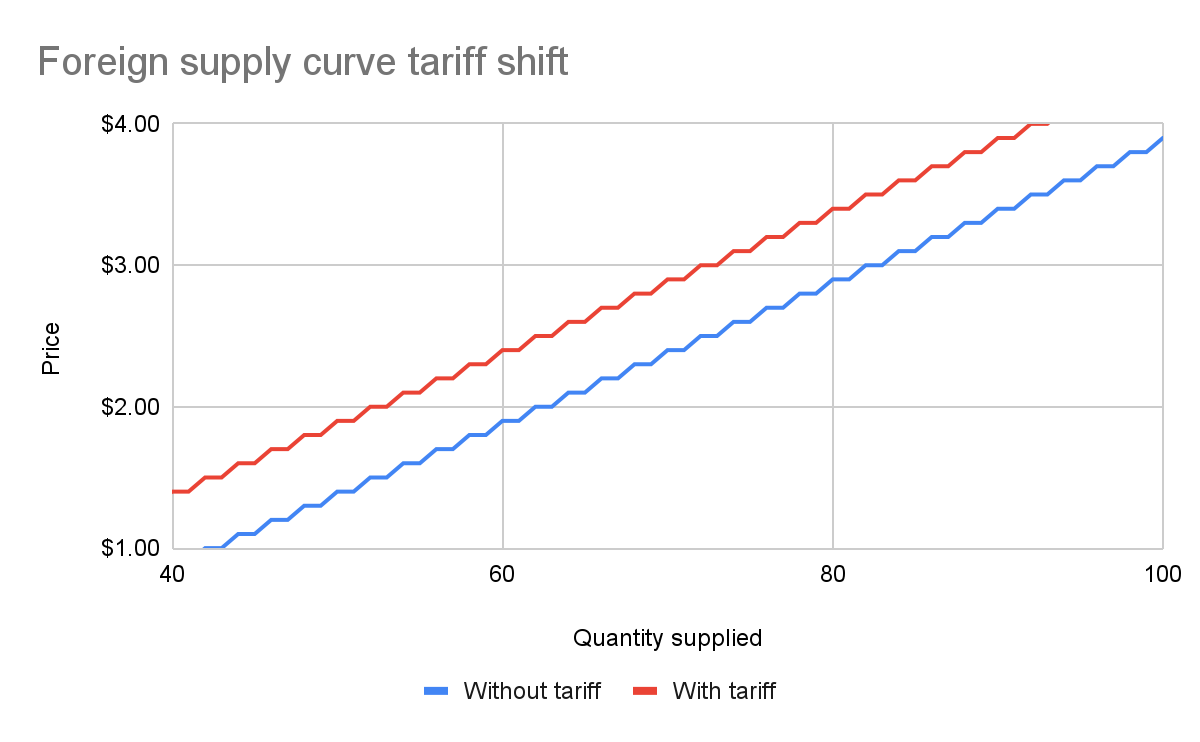
With the tariff in place, for each quantity level, the price at which the seller will sell is $0.50 higher than before the tariff. That makes sense: if I was previously willing to sell my 82nd apple for $3, I would now need to charge $3.50 for that apple to cover the cost of the tariff. We see this as the tariff “pushing up” or “pushing left” the original supply curve.
We can add this new supply curve to our existing (unchanged) supply curve for domestic-only sellers, and we end up with a result like this:
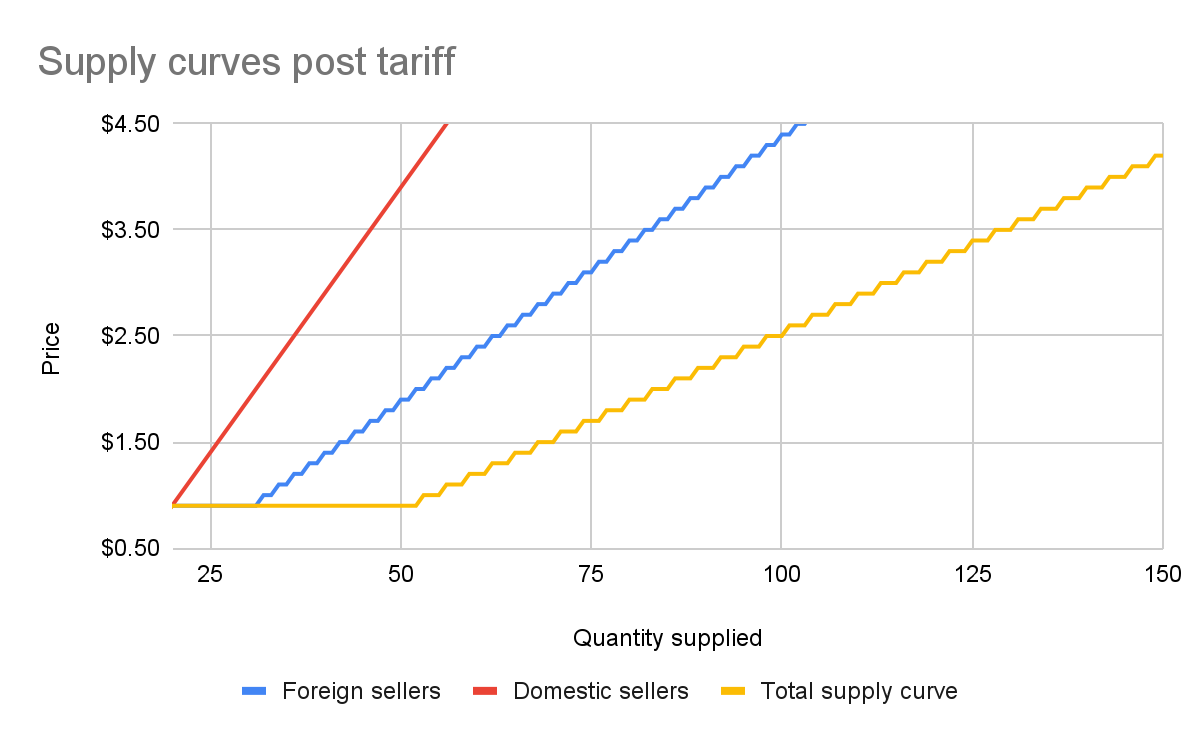
The total supply curve adds up the individual foreign and domestic supply curves. At each price point, we add up the total quantity each group would be willing to sell to determine the total quantity supplied for each price point. Once we have that cumulative supply curve defined, we can produce an updated supply-and-demand chart including the tariff:
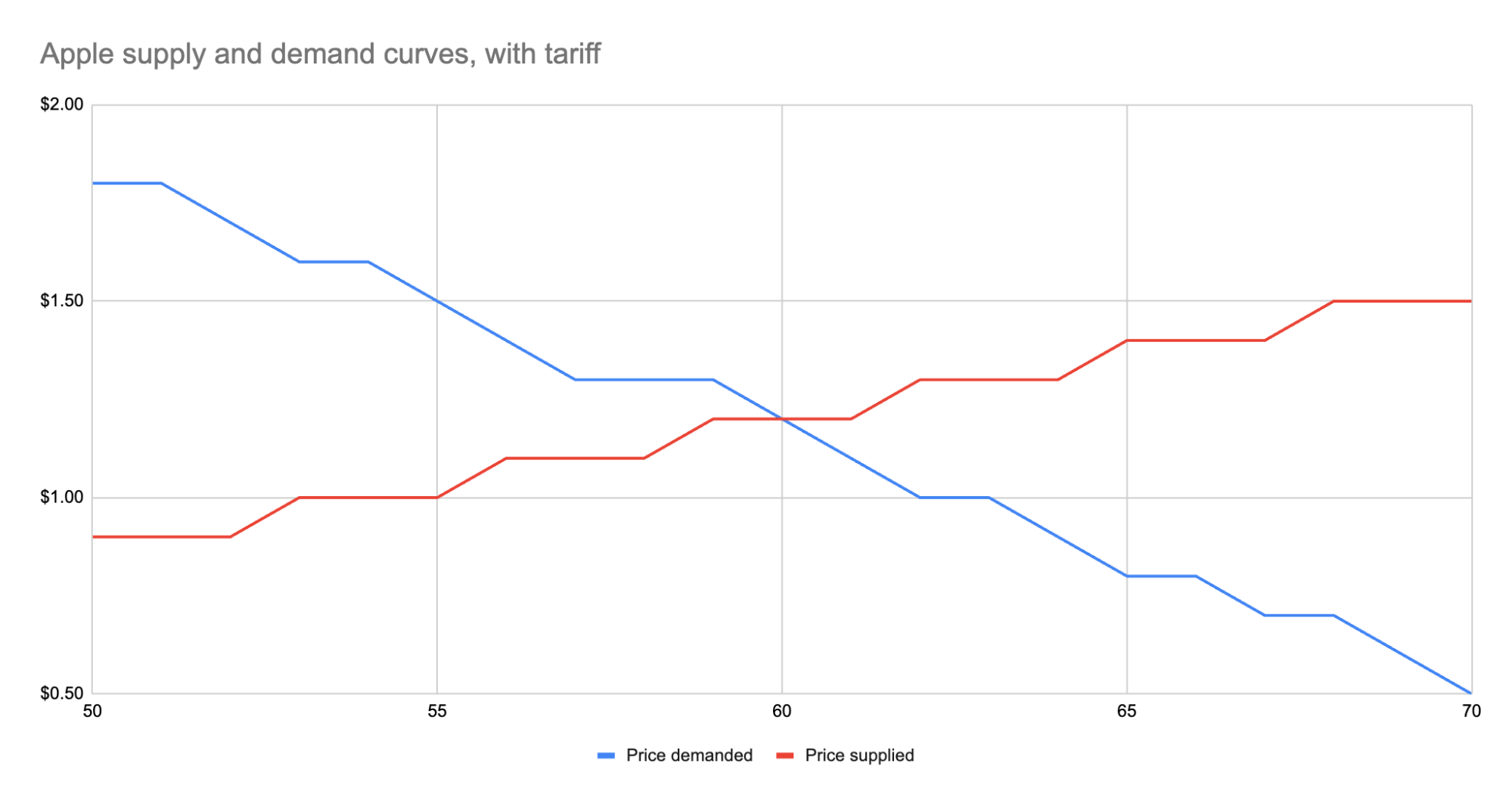
As we can see, the equilibrium has shifted:
* The equilibrium price paid by consumers has risen from $1 to $1.20.
* The total number of apples purchased has dropped from 63 apples to 60 apples.
* Consumers therefore received 3 less apples. They spent $72 for these 60 apples, whereas previously they spent $63 for 3 more apples, a definite decrease in consumer surplus.
* Foreign producers sold 36 of those apples (see the raw data in the linked Google Sheet), for a gross revenue of $43.20. However, they also need to pay the tariff to the US government, which accounts for $18, meaning they only receive $25.20 post-tariff. Previously, they sold 42 apples at $1 each with no tariff to be paid, meaning they took home $42.
* Domestic producers sold the remaining 24 apples at $1.20, giving them a revenue of $28.80. Since they don’t pay the tariff, they take home all of that money. By contrast, previously, they sold 21 apples at $1, for a take-home of $21.
* The government receives $0.50 for each of the 60 apples sold, or in other words receives $30 in revenue it wouldn’t have received otherwise.
We could be more specific about the surpluses, and calculate the actual areas for consumer surplus, producer surplus, inefficiency from the tariff, and government revenue from the tariff. But I won’t bother, as those calculations get slightly more involved. Instead, let’s just look at the aggregate outcomes:
* Consumers were unquestionably hurt. Their price paid went up by $0.20 per apple, and received less apples.
* Foreign producers were also hurt. Their price received went down from the original $1 to the new post-tariff price of $1.20, minus the $0.50 tariff. In other words: foreign producers only receive $0.70 per apple now. This hurt can be mitigated by shifting sales to other countries without a tariff, but the pain will exist regardless.
* Domestic producers scored. They can sell less apples and make more revenue doing it.
* And the government walked away with an extra $30.
Hopefully you now see the answer to the original questions. Importantly, while the government imposed a $0.50 tariff, neither side fully absorbed that cost. Consumers paid a bit more, foreign producers received a bit less. The exact details of how that tariff was split across the groups is mediated by the relevant supply and demand curves of each group. If you want to learn more about this, the relevant search term is “price elasticity,” or how much a group’s quantity supplied or demanded will change based on changes in the price.
## Other taxes
Most taxes are some kind of a tax on trade. Tariffs on apples is an obvious one. But the same applies to income tax (taxing the worker for the trade of labor for money) or payroll tax (same thing, just taxing the employer instead). Interestingly, you can use the same model for analyzing things like tax incentives. For example, if the government decided to subsidize domestic apple production by giving the domestic producers a $0.50 bonus for each apple they sell, we would end up with a similar kind of analysis, except instead of the foreign supply curve shifting up, we’d see the domestic supply curve shifting down.
And generally speaking, this is what you’ll *always* see with government involvement in the economy. It will result in disrupting an existing equilibrium, letting the market readjust to a new equilibrium, and incentivization of some behavior, causing some people to benefit and others to lose out. We saw with the apple tariff, domestic producers and the government benefited while others lost.
You can see the reverse though with tax incentives. If I give a tax incentive of providing a deduction (not paying income tax) for preschool, we would end up with:
* Government needs to make up the difference in tax revenue, either by raising taxes on others or printing more money (leading to inflation). Either way, those paying the tax or those holding government debased currency will pay a price.
* Those people who don’t use the preschool deduction will receive no benefit, so they simply pay a cost.
* Those who do use the preschool deduction will end up paying less on tax+preschool than they would have otherwise.
This analysis is fully amoral. It’s not saying whether providing subsidized preschool is a good thing or not, it simply tells you where the costs will be felt, and points out that such government interference in free economic choice does result in inefficiencies in the system. Once you have that knowledge, you’re more well educated on making a decision about whether the costs of government intervention are worth the benefits.
-

@ 9e69e420:d12360c2
2025-02-01 11:16:04

Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-

@ 97c70a44:ad98e322
2025-01-30 17:15:37
There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test.
In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go.
# It uses nostr
The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol.
Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key.
In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along.
In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim.
# It leverages nostr
Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app".
This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back.
Some examples might include:
- Using nostr signers to encrypt or sign data, and then store that data on a proprietary server.
- Using nostr relays as a kind of low-code backend, but using proprietary event payloads.
- Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you.
An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem.
In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering.
# It complements nostr
Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role.
One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense.
Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)?
A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs.
To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen.
# It embodies nostr
Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate.
This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product?
To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the *protocol*, while apps that benefit nostr exclusively via network effect are integrated into nostr the *network*. An app that does both things is working in symbiosis with nostr as a whole.
An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem:
- In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors.
- In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for.
Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency _as nostr users_.
If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states:
> Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions.
These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers.
_As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria._
Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type".
To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well,
- There is a [spec](https://github.com/nostr-protocol/nips/pull/1190) for forms and responses, which means that...
- Multiple clients can implement the same data format, allowing for credible exit and user choice, even of...
- Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does...
- Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to...
- Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost".
Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr.
# It supports nostr
Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually).
This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content?
In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together.
A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own.
So while I might hesitate to call many of these things "apps", they are certainly "nostr".
# Appendix: it smells like a NINO
So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr.
You app might be a NINO if:
- There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind)
- There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository)
- Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr
- Your NIP relies on trusted third (or first) parties
- There's only one implementation of your NIP (yours)
- Your core value proposition doesn't depend on relays, events, or nostr identities
- One or more relay urls are hard-coded into the source code
- Your app depends on a specific relay implementation to work (*ahem*, relay29)
- You don't validate event signatures
- You don't publish events to relays you don't control
- You don't read events from relays you don't control
- You use legacy web services to solve problems, rather than nostr-native solutions
- You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app
- You don't use NIP 89 to discover clients and services
- You haven't published a NIP 89 listing for your app
- You don't leverage your users' web of trust for filtering out spam
- You don't respect your users' mute lists
- You try to "own" your users' data
Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product.
If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation:
- Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine.
- Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc.
- Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats.
- Think your idea is a good one? Talk to other devs or open a PR to the [nips repo](https://github.com/nostr-protocol/nips). No one can adopt your NIP if they don't know about it.
- Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated.
- Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask!
I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV.
-

@ 9e69e420:d12360c2
2025-01-30 12:23:04
Tech stocks have taken a hit globally after China's DeepSeek launched a competitive AI chatbot at a much lower cost than US counterparts. This has stirred market fears of a $1.2 trillion loss across tech companies when trading opens in New York.
DeepSeek’s chatbot quickly topped download charts and surprised experts with its capabilities, developed for only $5.6 million.
The Nasdaq dropped over 3% in premarket trading, with major firms like Nvidia falling more than 10%. SoftBank also saw losses shortly after investing in a significant US AI venture.
Venture capitalist Marc Andreessen called it “AI’s Sputnik moment,” highlighting its potential impact on the industry.
![] (https://www.telegraph.co.uk/content/dam/business/2025/01/27/TELEMMGLPICT000409807198_17379939060750_trans_NvBQzQNjv4BqgsaO8O78rhmZrDxTlQBjdGLvJF5WfpqnBZShRL_tOZw.jpeg)
-

@ bcbb3e40:a494e501
2025-03-31 15:23:12
|[](https://www.hiperbolajanus.com/libros/esoterismo-berard-fata/)|
|:-:|
|[BÉRARD, Bruno y LA FATA, Aldo; _¿Qué es el esoterismo?: Entre verdades y falsificacioines_; Hipérbola Janus, 2025](https://hiperbolajanus.com/libros/esoterismo-berard-fata/)|
Nos complace presentar al lector en lengua española una novedad de primer orden, y sobre un tema que viene siendo objeto de interés por parte de nuestra línea editorial, como es el esoterismo, que hemos abordado recientemente a través de un nuevo recopilatorio de la obra evoliana en [*Ensayos filosóficos, esotéricos y religiosos 1925-1931*](https://hiperbolajanus.com/posts/presentacion-ensayos-filosoficos-evola/), donde hemos tratado de rescatar los textos de las primeras etapas en la formulación del pensamiento del Maestro Romano. No obstante, no es la primera aventura que hemos emprendido en este terreno, siempre complejo y acompañado de la etiqueta, popular y quizás vulgarizada, de lo «misterioso» y lo «oculto», aunque no somos nada sospechosos en ese sentido por banalizar o tratar de ofrecer un enfoque puramente literario del asunto, y ni mucho menos de simpatizar con aquellas vías que entroncan con el *New age*, donde las mixtificaciones y la voluntad de convertir el fenómeno esotérico en un producto de consumo más, como demanda el mercado, para satisfacer demandas materiales o simples modas de una masa sobresocializada son norma habitual.
Podríamos citar multitud de obras que están presentes en nuestro catálogo, como son [*El pensamiento esotérico de Leonardo*](https://hiperbolajanus.com/posts/presentacion-pensamiento-esoterico-leonardo-paul-vulliaud/), de **Paul Vulliaud**, [*El mundo mágico de los héroes*](https://hiperbolajanus.com/posts/mundo-magico-heroes-cesare-riviera/), de **Cesare della Riviera**, una joya del esoterismo italiano del siglo XVII, en [*El maestro de la tradición perenne*](https://hiperbolajanus.com/posts/rene-guenon-maestro-tradicion-perenne/), de **René Guénon**, o en el ensayo de **Gianluca Marletta** [*OVNIS y alienígenas. Origen, historia y prodigio de una pseudorreligión*](https://hiperbolajanus.com/posts/ovnis-alienigenas-gianluca-marletta/), un ensayo de notable originalidad donde se abordan aspectos esotéricos, aunque sea de un modo más tangencial. También en la literatura, con la obra del gran mitólogo y literato **Boris Nad**, [*Una historia de Agartha*](https://hiperbolajanus.com/posts/historia-agartha-boris-nad/) y [*La muerte púrpura*](https://hiperbolajanus.com/posts/gustav-meyrink/) de **Gustav Meyrink** encontramos nuevas referencias al ámbito esotérico. De modo que podemos concluir en que el esoterismo forma parte esencial de nuestras publicaciones e intereses como editores, y contribuimos activamente a su difusión.
|[](https://www.hiperbolajanus.com/libros/ensayos-filosoficos-esotericos-religiosos-evola/)|
|:-:|
|[EVOLA, Julius; _Ensayos filosóficos, esotéricos y religiosos: 1925-1931_, Hiperbola Janus, 2024](https://www.hiperbolajanus.com/libros/ensayos-filosoficos-esotericos-religiosos-evola/)|
# Una obra original
Por eso la presente obra, la que nos disponemos a presentar, cuyo título es *¿Qué es el esoterismo?: Entre verdades y falsificaciones*, de **Bruno Bérard** y **Aldo La Fata**, viene a ser una obra muy necesaria y clarificadora en la comprensión del esoterismo en todas sus dimensiones, en la complejidad de sus particulares, y en sus múltiples manifestaciones. Quizás en el mundo de habla hispana el esoterismo es un fenómeno que no ha obtenido su merecida atención, y nuestros autores en este ámbito, como es el caso de un **Ramón Llull** entre otros, no sean objeto de la atención que merece, y las actividades esotéricas, a nivel de asociaciones, comunidades u otras formas de organización, tampoco sean especialmente conocidas, ni cuenten con una actividad reconocida. Es posible, como señala La Fata, que haya ciertas reticencias dentro del mundo católico, acostumbrado a la ortodoxia y la guía espiritual de la Iglesia, y que cualquier tipo de «desviación» hacia formas más individuales y «libres» de vivir ciertas formas iniciáticas, mucho más sutiles, provoquen el rechazo y la incomprensión general. No obstante, como también se encargan de aclarar nuestros autores, el esoterismo comprende una dimensión diferenciada, implica un esfuerzo que no todos están dispuestos a acometer, y finalmente, no es tampoco un camino de felicidad y de frutos seguros, implica una transformación interior y la asunción de unas prácticas y procedimientos que no son aptos para cualquiera. Digamos que el esoterismo es un camino, una vía, que a diferencia de las «religiones populares», exotéricas, supone un arduo camino que viene marcado por un principio vertical y aristocrático de la existencia, o al menos así queremos verlo nosotros. El incremento de la capacidad de discernimiento, aunar lo visible con lo invisible, y ser capaz de superar límites vedados al común, no por simple vanidad ni por «crecimiento personal», tal y como se concibe en las aburguesadas y decadentes sociedades actuales, sino como parte de un proceso de aprendizaje, de autoconocimiento y de liberación. No nos cabe duda alguna de la necesidad de restaurar los antiguos vínculos con lo Alto, las vías que quedaron cerradas y que nos han limitado progresivamente al exclusivo y estrecho ámbito de la materialidad.
|[](https://www.hiperbolajanus.com/libros/mundo-magico-heroes-cesare-riviera/)|
|:-:|
|[RIVIERA, Cesare della; _El mundo mágico de los héroes_; Hipérbola Janus, 2022](https://www.hiperbolajanus.com/libros/mundo-magico-heroes-cesare-riviera/)|
La obra emplea el recurso de la entrevista/diálogo, que aporta frescura y fluidez al texto «simplificando», o más bien haciendo más accesibles y comprensibles elementos relacionados con el esoterismo, que de otro modo resultarían excesivamente complejos para una parte del público lector poco familiarizado con la materia. Este dinamismo se ve complementado por la riqueza de matices e ideas que se van introduciendo de manera progresiva, evitando que el lector pueda verse abrumado por la avalancha de ideas y contenidos. Las preguntas de Bruno Bérard, siempre inteligentes, incisivas y pertinentes, además de ordenadas y bien estructuradas, favorecen la continuidad y el dinamismo en la exposición de los temas, ejerciendo de guía en la conversación. De ahí que el libro sea apto para diferentes niveles, tanto para aquellos que desconocen el esoterismo, como para quienes se encuentran familiarizados con el tema. Aldo La Fata, de acuerdo con su dilatada y extensa trayectoria en la materia, nos hace reflexiones teóricas de enorme valor, que entrelaza con su propia experiencia y trayectoria en el estudio del esoterismo. Sin lugar a dudas este aspecto nos permite ver una vertiente más humana e íntima, en la que se incluyen anécdotas personales y biográficas que siempre permiten una mayor conexión con el lector a través de la mezcla de hechos vitales y erudición teórica.
La entrevista que nos ofrecen Bruno Bérard y Aldo La Fata nos permite explorar la relación dialéctica que se genera entre el esoterismo y otros ámbitos como la religión, la ciencia o la filosofía. Todas las cuestiones se abordan desde enfoques muy concretos, abordando problemáticas particulares, que dan lugar a reflexiones más amplias evitando las simplificaciones e invitando a reflexiones mucho más profundas. De ahí la función de introducción y guía a la que nos venimos refiriendo.
Estos aspectos que acabamos de enumerar con anterioridad revelan un notable esfuerzo pedagógico por parte de los autores para acercarnos al estudio del esoterismo, nos aporta las herramientas necesarias, parafraseando el título de la obra, para discernir entre un verdadero esoterismo y sus falsificaciones.
Más allá de estos aspectos formales, que consideramos que es importante destacar, porque en ellos reside el éxito de la obra, en un planteamiento que resulta original, a la par que ameno y de gran interés, debemos considerar otros aspectos que hacen más referencia al contenido. *«¿Qué es el esoterismo? Entre verdades y falsificaciones»* pretende, como decíamos, clarificar qué es el esoterismo, cuales son sus particulares, sus características y atributos, su naturaleza más íntima, como fenómeno espiritual y filosófico en sus aspectos más profundos, que podemos remontar a épocas muy remotas y lejanas en el tiempo. Pero el esoterismo aparece en ocasiones fuertemente imbricado en otras estructuras de pensamiento, de tipo tradicional, como son las grandes religiones (Cristianismo, Islam, Judaísmo etc) y otros conceptos como la mística y la metafísica, cuyas relaciones hay que desentrañar.
# La importancia de René Guénon
Aldo La Fata nos libera desde el principio de posibles equívocos al enfatizar que el verdadero esoterismo no es una simple acumulación de conocimientos secretos o rituales exóticos, sino una vía de trascendencia espiritual basada en el rigor y la autenticidad. A este respecto [René Guénon aparece como uno de los grandes esoteristas de nuestro tiempo](https://hiperbolajanus.com/posts/rene-guenon-y-la-civilizacion-occidental/), en la medida que fue el gran intérprete y codificador de estos conocimientos, una figura que marcó un antes y un después en la comprensión de este ámbito, especialmente por su rigor conceptual y su capacidad para distinguir entre lo auténtico y lo falso en las tradiciones espirituales. A tal respecto podemos poner como ejemplo sus contundentes análisis de las corrientes ocultistas, especialmente del espiritismo o del teosofismo, en diferentes obras. Podemos decir a este respecto que Guénon hizo una distinción entre esoterismo y ocultismo, disociando el significado del primero de prácticas superficiales y desviadas, mientras que definió el esoterismo como una vía de conocimiento sagrado y trascendente. En este sentido fue una labor fundamental para evitar confusiones con mixtificaciones modernas y pseudoesoterismos como [aquellos relacionados con el *New Age*](https://hiperbolajanus.com/posts/nom-magos-negros/).
|[](https://www.hiperbolajanus.com/libros/maestro-tradicion-rene-guenon/)|
|:-:|
|[GUÉNON, René; _El Maestro de la Tradición Perenne: Antología de artículos guenonianos_; Hipérbola Janus, 2021](https://www.hiperbolajanus.com/libros/maestro-tradicion-rene-guenon/)|
Paralelamente, y con ello queremos dignificar la figura de René Guénon, el tradicionalista francés también nos abrió las fuentes de un vasto conocimiento espiritual, expresión de una «Tradición primordial», a cuyos orígenes prístinos siempre deberíamos aspirar, y [cuya impronta impregna por completo religiones, culturas y formas de civilización no modernas](https://hiperbolajanus.com/posts/el-reino-de-la-cantidad-y-los-signos-de/), claro está. Y otro elemento fundamental, y que en la presente obra se considera de vital importancia, es que René Guénon considera el esoterismo no como una vía interna propia de la religión, sino como una vía complementaria que permite acceder a la esencia divina más allá de las formas externas. Para Aldo La Fata no se trata de una mera referencia intelectual, sino una figura que marcó su propio rumbo dentro del estudio del esoterismo. A través de obras como *Los símbolos de la ciencia sagrada*, La Fata descubrió la profundidad y la coherencia del pensamiento guenoniano, así como la idea de que el esoterismo actúa como el «pegamento» que conecta todas las tradiciones espirituales. Esta visión le permitió entender el esoterismo como algo inseparable de la religión, aunque con una profundidad y una exigencia mayores.
# ¿Qué es el esoterismo?
El término esoterismo tiene sus raíces etimológicas en el griego *esôterikos*, que implica un «ir hacia dentro» y que se contrapone a una variante exterior que definimos como «exoterismo», que se encuentra más vinculado al ámbito de la religión. Se trata de un conocimiento que no atiende a un principio puramente intelectual y discursivo sino que apunta a una vivencia directa y sapiencial de lo trascendente. Lejos de la acumulación de saberes ocultos y rituales, lo que prima en la experiencia de lo esotérico es la conexión directa con lo trascendente y lo divino a través de la práctica espiritual.
De hecho hay tres aspectos que nuestros autores destacan a lo largo de la obra respecto al esoterismo, y que nos parecen fundamentales:
- **Interioridad**: Supone un movimiento continuo hacia el interior, de exploración e introspección, en el que se tratan de derribar límites y obstáculos. Atendiendo a un dinamismo que huye de lo fijo y de lo estático.
- **Profundización**: La búsqueda de significados más profundos tras la realidad cotidiana, buscando ir más allá de la pura exterioridad de las cosas
- **Relación con el exoterismo**: Podemos considerarlo opuesto en sentido relativo al esoterismo, como una dimensión más externa y visible de las religiones, aunque este último (el esoterismo), no puede sobrevivir sin el apoyo de una tradición religiosa.
En relación al último punto debemos destacar, como advierten Bérard y La Fata, que pese a todo no podemos entender el esoterismo como una parte de las religiones, sino que tiene su propia función y objetivos, que no es otro que el que ya hemos mencionado con anterioridad: establecer una conexión directa con la verdad que irradia del principio universal y divino.
|[](https://www.hiperbolajanus.com/libros/pensamiento_esoterico_leonardo_vinci_paul_vulliaud/)|
|:-:|
|[VULLIAUD, Paul; _El pensamiento esotérico de Leonardo da Vinci_; Hipérbola Janus, 2024](https://www.hiperbolajanus.com/libros/pensamiento_esoterico_leonardo_vinci_paul_vulliaud/)|
Otro aspecto interesante de la obra es el que nos habla de [las relaciones entre esoterismo y metafísica](https://hiperbolajanus.com/libros/metapolitica-tradicion-modernidad-julius-evola/), en el que el primero pretende ser también una vía de acceso al dominio del segundo. El esoterismo, como ya hemos visto, tiene como principal propósito trascender las categorías del mundo material para proyectarse en lo universal, y en este sentido comparte también objetivos con la metafísica, que pretende superar las limitaciones de la experiencia humana ordinaria y de acceder a las verdades primordiales que estructuran la realidad. Ambos apuntan a la raíz de todo lo existente, al absoluto. Las divergencias las hallamos en la forma o en el método para alcanzar estas verdades trascendentes, que en el caso del esoterismo nos remiten a símbolos, rituales y experiencias vivenciales que permiten al practicante interiorizar verdades universales.
De este modo, esoterismo y metafísica se nos presentan como realidades no opuestas, sino complementarias. La metafísica nos ofrece un marco conceptual y doctrinal para entender lo absoluto, mientras que el esoterismo se centra en su realización interna. En términos guenonianos, el esoterismo representa los aspectos operativos de la metafísica.
De modo que podemos decir que la metafísica aborda el tema trascendente desde una perspectiva conceptual, sin esa parte vivida de la experiencia en el conocimiento de lo universal. El esoterismo, por su parte, aporta esa contraparte que nos remite a la experiencia humana que permite al individuo acceder o ponerse en conexión con lo divino a través de su propio ser, de manera directa y vívida. Es un camino que el sujeto individual emprende para lograr una transformación interior.
Paralelamente, no podemos obviar dentro de todos estos procesos la participación de un elemento fundamental, como es la intuición suprarracional, que podríamos considerar como la herramienta que conecta al esoterista directamente con la fuente del conocimiento trascendente y universal, en lugar de hacerlo directamente a través de teorías o conceptos que siempre resultan más abstractos y difíciles de comprender en su vertiente más «discursiva». Al mismo tiempo, las relaciones que se establecen entre esoterismo y metafísica nos permiten poner en contacto las tradiciones religiosas con el conocimiento universal. Según La Fata, inspirándose en el legado de la obra de Frithjoff Schuon, cada tradición espiritual tiene una dimensión metafísica que puede ser comprendida y realizada a través del esoterismo, como un medio para acceder a la esencia inmutable de todas las formas religiosas.
Otro aspecto que esoterismo y metafísica comparten es la meta de superar la dualidad entre sujeto y objeto: Mientras que la metafísica conceptualiza esta unión como una verdad última, el esoterismo busca experimentarla directamente a través de la contemplación, el símbolo y la práctica espiritual.
# Los autores
||
|:-:|
|Aldo La Fata|
Aldo La Fata (1964) es un estudioso del esoterismo, el simbolismo y la mística religiosa, con una trayectoria de varias décadas dedicada al análisis y divulgación de estas disciplinas. Ha sido jefe de redacción de la revista *Metapolitica*, fundada por **Silvano Panunzio**, y actualmente dirige *Il Corriere Metapolitico*. Su trabajo destaca por una aproximación rigurosa y una mirada crítica a las corrientes contemporáneas del esoterismo, rescatando su sentido más profundo y tradicional. Entre sus obras más relevantes se encuentran *Silvano Panunzio: vita e pensiero* (2021) y *Nella luce dei libri* (2022), donde explora la intersección entre espiritualidad, simbolismo y pensamiento tradicional.
||
|:-:|
|Bruno Bérard|
Bruno Bérard (1958), es doctor en Religiones y Sistemas de Pensamiento por la École Pratique des Hautes Études (EPHE), es un destacado especialista en metafísica. Autor de múltiples ensayos, ha desarrollado una profunda reflexión sobre la naturaleza del conocimiento espiritual y su relación con las tradiciones religiosas. Algunas de sus obras más importantes, traducidas a diversas lenguas, incluyen A *Metaphysics of the Christian Mystery* (2018) y *Métaphysique du paradoxe* (2019). Actualmente, dirige la colección *Métaphysique au quotidien* en la editorial L’Harmattan de París, consolidándose como una referencia en el estudio de la metafísica contemporánea.
En *¿Qué es el esoterismo?: Entre verdades y falsificaciones*, asistimos a una presentación del tema tratado desde un conocimiento profundo y dilatado del tema, en la que ambos autores combinan la experiencia y el conocimiento que atesoran sobre el esoterismo y otros temas anejos, ofreciéndonos sus interpretaciones y enfoques particulares, y al mismo tiempo mostrando una gran capacidad de síntesis en la exposición de los temas tratados, que se inscriben en una multitud de tradiciones religiosas y espirituales de enorme complejidad. En este último punto reside también gran parte del valor de la obra, que constituye una novedad editorial especialmente relevante en su ámbito en lengua hispana.
---
**Artículo original**: Hipérbola Janus, [_Presentación de «¿Qué es el esoterismo?: Entre verdades y falsificaciones»_](https://www.hiperbolajanus.com/posts/presentacion-esoterismo-berard-lafata/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/presentacion-esoterismo-berard-lafata/), 6/Feb/2025
-

@ 9e69e420:d12360c2
2025-01-30 12:13:39
Salwan Momika, a Christian Iraqi known for burning the Koran in Sweden, was shot dead during a TikTok livestream in an apartment in Sodertalje. The 38-year-old sparked outrage in the Muslim community for his demonstrations, leading to global condemnation. After being rushed to the hospital, he was pronounced dead.
Authorities arrested five individuals in connection with the incident. Momika's death comes days before a court ruling on his possible incitement of ethnic hatred. The incident highlights the tensions surrounding free speech and religious sentiments, intensifying after his controversial protests in 2023.
[Sauce](https://www.dailymail.co.uk/news/article-14341423/Christian-Iraqi-burnt-Koran-Sweden-shot-dead.html)
-

@ 0fa80bd3:ea7325de
2025-01-30 04:28:30
**"Degeneration"** or **"Вырождение"**
![[photo_2025-01-29 23.23.15.jpeg]]
A once-functional object, now eroded by time and human intervention, stripped of its original purpose. Layers of presence accumulate—marks, alterations, traces of intent—until the very essence is obscured. Restoration is paradoxical: to reclaim, one must erase. Yet erasure is an impossibility, for to remove these imprints is to deny the existence of those who shaped them.
The work stands as a meditation on entropy, memory, and the irreversible dialogue between creation and decay.
-

@ 0fa80bd3:ea7325de
2025-01-29 15:43:42
Lyn Alden - биткойн евангелист или евангелистка, я пока не понял
```
npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83a
```
Thomas Pacchia - PubKey owner - X - @tpacchia
```
npub1xy6exlg37pw84cpyj05c2pdgv86hr25cxn0g7aa8g8a6v97mhduqeuhgpl
```
calvadev - Shopstr
```
npub16dhgpql60vmd4mnydjut87vla23a38j689jssaqlqqlzrtqtd0kqex0nkq
```
Calle - Cashu founder
```
npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vg
```
Джек Дорси
```
npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m
```
21 ideas
```
npub1lm3f47nzyf0rjp6fsl4qlnkmzed4uj4h2gnf2vhe3l3mrj85vqks6z3c7l
```
Много адресов. Хз кто надо сортировать
```
https://github.com/aitechguy/nostr-address-book
```
ФиатДжеф - создатель Ностр - https://github.com/fiatjaf
```
npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6
```
EVAN KALOUDIS Zues wallet
```
npub19kv88vjm7tw6v9qksn2y6h4hdt6e79nh3zjcud36k9n3lmlwsleqwte2qd
```
Программер Коди https://github.com/CodyTseng/nostr-relay
```
npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl
```
Anna Chekhovich - Managing Bitcoin at The Anti-Corruption Foundation
https://x.com/AnyaChekhovich
```
npub1y2st7rp54277hyd2usw6shy3kxprnmpvhkezmldp7vhl7hp920aq9cfyr7
```
-

@ bcbb3e40:a494e501
2025-03-31 15:02:58
Traducción por Francisco de la Torre.
||
|:-:|
|Los representantes de la derecha sionista europea que forman parte de «Patriots» reunidos en Bruselas el pasado mes de diciembre de 2024.|
Entre los efectos que probablemente producirá en Europa la nueva administración estadounidense, es previsible [el fortalecimiento del ala derecha del colaboracionismo atlantista](https://hiperbolajanus.com/posts/mos-maiorum-8/) que, después de haberse posicionado decididamente a favor de Donald Trump durante su presidencia 2017-2021, en el transcurso de la administración Biden abogó fervientemente por su regreso a la Casa Blanca y acogió su victoria electoral con gran júbilo. A finales de octubre de 2024, en el grandioso [mitin preelectoral a favor de Trump](https://hiperbolajanus.com/posts/adios-woke-que-viene-ahora/) celebrado en el Madison Square Garden de Nueva York, asistió una representante del grupo parlamentario europeo *Patriots for Europe*, que viajó a Estados Unidos para esa ocasión especial. En un vídeo publicado en la página X (antes twitter) de los *Patriots*, varios eurodiputados del mencionado grupo expresaron su identidad con los puntos de vista de Trump y auspiciando su reelección: el austriaco Harald Vilimsky (*Freiheitliche Partei Österreichs*), el checo Ondrej Knotek (*Año 2011*) el español Jorge Buxade (*Vox*), el holandés Tom Vandendriesche (*Vlaams Belang*), la polaca Anna Bryłka (*Ruch Narodowy*) y, por Hungría, Tamás Deutsch (*Fidesz*).
Este último es, sin duda, la personalidad más eminente del grupo de los *Patriots* que viajaron a Nueva York: originario de una familia judía de Budapest, en 1988 Tamás Deutsch junto con Viktor Orbán están entre los fundadores de *Fidesz* —*Fiatal Demokraták Szövetsége* (Alianza de los jóvenes demócratas), en la que ocupó el cargo de vicepresidente. El *Fidesz* ha tejido durante mucho tiempo una red de lazos con el Partido Republicano de los Estados Unidos y con el think tank conservador *Heritage Foundation*, mientras que el gobierno de Viktor Orbán organizó las tres últimas ediciones anuales de la CPAC en Hungría (*Conservative Political Action Conference*), un encuentro de políticos de derechas de varios países[^1].
*Patriots for Europe* o *Patriots.eu*, denominación que recuerda al de los misiles aire-tierra estadounidenses (el *MIM-104 Patriots*), es, por tanto, el nombre oficial del grupo político de la derecha liberal-conservadora, populista y euroescéptica, nacido en julio de 2024 (primero como alianza y luego como grupo parlamentario europeo) por iniciativa del primer ministro húngaro Viktor Orbán, el exprimer ministro checo Andrej Babiŝ y del exministro del interior austriaco Herbert Kickl. Como representantes de sus respectivos partidos (*Fidesz*, *Año 2011*, *Freiheitliche Partei Österreichs*), Orbán, Babiŝ y Kickl firmaron un texto ideológico titulado: *A Patriotic Manifesto for a European Future*[^2], según la cual la única política europea legítima es aquella que, enraizada en la pluralidad de las diferentes naciones, proteja su herencia grecorromana-judeocristiana preservando su identidad, tradiciones y costumbres.
Al núcleo inicial de los *Patriots* se unió el partido portugués *¡Arriva!* (*¡Chega!*), el Partido húngaro Popular Demócrata Cristiano (*Kereszténydemokrata Néppárt*), el partido español *Vox*, el Partido por la Libertad (*Partij voor de Vrijheid*) holandés, el Partido Popular Danés (*Dansk Folkeparti*), el interés Flamenco (*Vlaams Belang*), la Reunión Nacional (*Rassemblement National*) francés y, por Italia, la Liga para Primer Ministro Salvini.
Constituido formalmente, el grupo parlamentario recibió una posterior adhesión del diputado griego de *Voz de la Razón* (*Foní Logikis*), del diputado de *Primero Letonia* (*Letvija pirmajâ prohibir*), de los dos diputados del Movimiento Nacional polaco (*Ruch Narodowy*) y de los dos diputados checos del Juramento (*Přísaha*) y de los Automovilistas por sí mismos (*Motoristé sollozoê*). Presidente del grupo parlamentario *Patriots.eu*, que cuenta con un total de ochenta y seis diputados[^3], es Jordan Bardella, presidente de la *Rassemblement National*; pero la personalidad más notable y prestigiosa de los *Patriots* es, sin duda, el primer ministro húngaro Viktor Orbán.
En cuanto a la línea de política exterior seguida por Viktor Orbán, cabe recordar que fue durante su primer mandato, en 1989, cuando Hungría se unió a la OTAN junto con la República Checa y Polonia. La pertenencia a la organización militar de la Alianza Atlántica implicó la participación húngara en la guerra de Kosovo en Yugoslavia, así como la contribución de Hungría en las misiones de la ISAF y en la guerra en Irak en apoyo de la intervención estadounidense. Por otro lado, no deja de ser significativo que en junio de 2011, durante la visita de Condoleezza Rice a Budapest, se inaugurara una estatua del presidente estadounidense Ronald Reagan en la céntrica Plaza de la Libertad (*Szabadság tér*). «Hoy —dijo Orbán en esa ocasión— erigimos aquí una estatua al hombre, al líder, que cambió y renovó este mundo [creando un nuevo mundo para nosotros en Europa Central](https://hiperbolajanus.com/posts/presentacion-despues-virus-boris-nad/), un hombre que creía en la libertad, en la fuerza moral de los hombres libres, y creía que los muros que obstruyen el camino a la libertad pueden ser derribados».
En los años de la primera administración Trump, Orbán estableció una relación privilegiada con la Casa Blanca: en 2019 fue recibido calurosamente por el presidente estadounidense, quien [declaró su apoyo al «soberanismo» europeo,](https://hiperbolajanus.com/libros/mos-maiorum-7/) del que Orbán era ya el exponente más puntero. El primer ministro húngaro, que más tarde expresó varias veces la esperanza de volver a ver a Trump como líder de los Estados Unidos, se reunió con él de nuevo en Mar-a-Lago de Palm Beach en marzo de 2024 y al final de la visita escribió en una publicación: «¡Hacer que América vuelva a ser grande, señor presidente!»[^4].
El entendimiento entre Trump y Orbán fue favorecido por Benjamin Netanyahu, quien ha tenido una estrecha relación con el actual primer ministro húngaro desde 2005, cuando Orbán estaba en la oposición y Netanyahu era ministro de Finanzas. Esta relación, que Orbán ha utilizado para neutralizar las iniciativas hostiles de las ONG’s de Soros (quien financió a *Fidesz* desde 1992 a 1999), ha acentuado progresivamente la posición proisraelí de Budapest, hasta el punto que Hungría junto a Austria, Croacia y República Checa, se han alineado con Estados Unidos e Israel votando en contra de la resolución propuesta por la ONU para el alto el fuego en la Franja de Gaza. Cuando László Toroczkai, jefe del partido *Mi Hazánk* (Nuestra Patria), preguntó a Orbán en el Parlamento por qué Hungría había votado en contra, el primer ministro le respondió: «La política exterior es complicada, enfréntate solo si entiendes de lo que estamos hablando»[^5].
El presidente de *Patriots*, Jordan Bardella, no es menos pro-sionista. «Reconocer un Estado palestino significaría reconocer el terrorismo», dijo Bardella, quien antes de las elecciones francesas había asegurado que, si llegaba a ser primer ministro, sería «un escudo para los compatriotas judíos contra un islamismo que no solo quiere separar la República, sino conquistarla»[^6]. Por su parte, Marine Le Pen, madrina política de Bardella, declaró: «Es absolutamente legítimo que Israel quiera erradicar al grupo terrorista armado Hamas y que se dote de medios para hacerlo»[^7].
En cuanto a la Liga de Salvini como primer ministro, sus posiciones pro-trumpistas y pro-sionistas siempre se han caracterizado por un extremismo descarado. «Nunca he ocultado —dijo Salvini antes de las elecciones estadounidenses— mi esperanza en una victoria republicana, por mil razones (...) hablamos [con Trump] a más tardar hace unas semanas. Nunca he ocultado mi simpatía humana y mi sintonía cultural»[^8]. Y sobre el genocidio en curso en Palestina, Salvini dijo: «Nuestros pensamientos están con el pueblo israelí (...) Recordar siempre el derecho de Israel a existir, a defenderse y a convivir finalmente en paz con sus pueblos vecinos, contra el horror del terrorismo islámico»[^9]. El 6 de octubre de 2024, al final de su discurso desde el escenario de Pontida, Salvini posó para una foto con los *Patriots* presentes en la manifestación de la Liga Norte: además de Viktor Orbán, estuvieron el holandés Geert Wilders, el portugués André Ventura, la austriaca Marlene Svazek, el español Antonio Fúster y el general Roberto Vannacci. Enviaron mensajes en vídeo de apoyo y solidaridad tanto Jordán Bardella en nombre de *Rassemblement national* como el ex-presidente brasileño Jair Bolsonaro.
También Geert Wilders (*Partij voor de Vrijheid*), que en 2009 recibió el Premio Oriana Fallaci por producir un cortometraje de propaganda antiislámica, es conocido también por su extremismo prosionista. «Jerusalén, Judea y Samaria —en su opinión— son todas de Israel (...) La patria de los palestinos es el Reino de Jordania (...) Obama y Kerry deben dejar de criticar a Israel por los asentamientos. Judea y Samaria pertenecen a los israelíes»[^10]. En el programa de Wilders, «distinguiéndose durante dos décadas por su lucha contra la islamización —escribe complacido un sitio web sionista— está también el reconocimiento de Jerusalén como capital de Israel, con el traslado de la embajada holandesa»[^11].
André Ventura, presidente de *¡Chega!*, reiteró en Polonia la posición prosionista de su partido, declarando convencido: «Estamos con Israel y permaneceremos junto a Israel en esta batalla por los derechos humanos y la democracia»[^12]. A quienes lo comparan con Donald Trump y Jair Bolsonaro, André Ventura responde: «Estoy acostumbrado a estas comparaciones. Estas son las ideas en las que creo»[^13]. En cuanto a la guerra en Ucrania, el líder de la lista *¡Chega!* en las elecciones europeas, Antonio Tânger Corrêa, dijo que «la derrota de Ucrania sería la derrota de todo Occidente y de Portugal, en caso de extrema necesidad»[^14], enviarían a sus tropas.
Marlene Svazek representó a la *Freiheitliche Partei Österreichs* en Pontida, cuyos «excelentes contactos»[^15] con la derecha israelí están garantizados por David Lasar, miembro del Consejo Nacional (*Nationalrat*) del partido austriaco. Lasar no es el único judío en el FPÖ: también es judío el ex-secretario general del partido y ex-parlamentario europeo Peter Sichrovsky, quien ha negado ser un agente del Mossad, pero ha admitido haber tenido «muchas reuniones con funcionarios israelís»[^16].
José Antonio Fúster es el nuevo presidente de *Vox* Madrid. El jefe del partido que lo representa, Santiago Abascal, encabezó una delegación a Israel en 2023 que se reunió con dos ministros de Tel Aviv. «Durante la visita, Abascal ha transmitido el apoyo y la solidaridad de España al Primer Ministro israelí Benjamin Netanyahu, y ha defendido la urgente necesidad de acabar con Hamas que, según Abascal, es un grupo terrorista que «encarna el mal absoluto»[^17]. Tras la reunión de la delegación de *Vox* con Netanyahu, el candidato electoral Jorge Buxadé Villalba afirmó que las acciones genocidas cometidas por el régimen sionista en la Franja de Gaza son «operaciones antiterroristas» que deben continuar «hasta que no quede ni un solo terrorista»[^18].
En cuanto a Roberto Vannacci, elegido diputado del Parlamento Europeo en las listas de la Liga por Salvini, su currículum vitae *patriot* puede jactarse de una participación activa en las operaciones de EE.UU. en Oriente Medio. El general comandó durante dos turnos (2005-2006) el *Special Forces Task Group* en Irak y fue el primer comandante de la *Task Force 45* en Afganistán en 2013, poco antes de la transición de la *International Security Assistance Force* a la *Resolute Support Mission*, Vannacci asumió el cargo de jefe del Estado Mayor de las fuerzas especiales de la OTAN, «una organización que ha garantizado la paz durante más de cincuenta años, una alianza política y militar que ha funcionado bien»[^19]. Habiendo prestado sus servicios a los Estados Unidos «para la estabilización de Irak»[^20] como *Deputy Commanding General* y *Director of Training*, el 21 de agosto de 2018, Vannacci fue galardonado con la *Legion of Merit*, la condecoración militar estadounidense creada por el presidente Franklin D. Roosevelt. Su consigna antes y después de la elección de Trump ha sido: «*Go, Donald, go!»*.
[^1]: Cfr. C. Mutti, *Alla destra degli USA*, «Eurasia» 1/2023.
[^2]: Después de la confluencia de los grupos de *Identity and Democracy* en el grupo de *Patriots*, se aprobó una nueva versión del manifiesto político. Véase [https://patriots.eu/manifesto](https://patriots.eu/manifesto)
[^3]: Freiheitliche Partei Österreichs (Austria), 6; Vlaams Belang (Bélgica), 3; Dansk Folkeparti (Dinamarca), 1; Rassemblement National (Francia), 30; Foni Logikis (Grecia), 1; Fidesz - Magyar Polgári Szövetség (Hungría), 10; Kereszténydemokrata Néppárt (Hungría), 1; Liga para Salvini Premier (Italia), 8; Letvija primajâ vietâ (Letonia), 1; Partij voor de Vrijheid (Países Bajos), 6; Ruch Narodowy (Polonia), 2; ¡Chega! (Portugal), 2; ANO (República Checa), 7; Automovilistaé sobê (República Checa), 1; Přísaha (República Checa), 1; Vox (España), 6.
[^4]: Angela Napoletano, *La «visita». Orbán incorona Trump: «Lui è il presidente della pace»*, avvenire.it, 9 marzo 2024.
[^5]: András Dezsô, *The roots of Orbán’s strong bond with Israel and its PM*, [https://balkaninsight.com](https://balkaninsight.com), 14 de noviembre de 2023.
[^6]: Bardella, «*riconoscere Palestina è riconoscere terrorismo*». «*Sarò uno scudo per i nostri connazionali ebrei*», ANSA, 26/6/2024.
[^7]: Mauro Zanon, *Sorpresa, lo «scudo» degli ebrei in Francia è il partito della Le Pen*, [tempi.it](https://tempi.it/), 27 de octubre de 2023.
[^8]: Stefano Baldolini, *Salvina punta su Trump: «Spero che vinca. Andrò negli Usa prima del voto». Tensioni con Meloni? «Governo durerà 5 anni»*, [repubblica.it](https://repubblica.it), 13 de julio de 2024.
[^9]: Nova.News, 7 de octubre de 2024.
[^10]: *Elezioni in Olanda, che è il sovranista Wilders: anti-Islam, contro l’Ue e sostenitore del Grande Israele*, [www.open.online](http://www.open.online), 23 de noviembre de 2023.
[^11]: [www.informazionecorretta.com](http://www.informazionecorretta.com/), 26 de octubre de 2024.
[^12]: [www.agenzianova.com](http://www.agenzianova.com), 6 de octubre de 2024.
[^13]: *Especial: André Ventura. «Sou contra o aborto mas nunca condenaria uma mulher que aborta»*, «Jornal SOL», 12 de julio de 2022.
[^14]: *Ventura admite tropas portuguesas na Ucrânia e tem uma posição clara sobre Putin*, «CNN Portugal», 11 de marzo de 2024.
[^15]: Sophie Makris, *Austria’s Jews wary of far-right charm offensive*, [www.timeofisrael.com](http://www.timeofisrael.com), 3 de marzo de 2019.
[^16]: Yossi Melman, *Sichrovsky Denies He Was a Mossad Agent*, [www.haaretz.com](http://www.haaretz.com), 3 de junio de 2005.
[^17]: Fernando Heller, *Spagna: il leader di Vox pretende le scuse di Sánchez per aver messo in dubbio l’offensiva israeliana contro Hamas*, [https://euractiv.it](https://euractiv.it), 6 de diciembre de 2023.
[^18]: *El ultraderechista Vox defiende los ataques de Israel en Gaza tras la polémica reunión con Netanyahu*, euronews, 29 de mayo de 2024.
[^19]: Bruno Vespa, *Vannacci: «Dopo l’Ue tornerei nell’esercito»*, «La Verità», 30 de octubre de 2024, p. 7.
[^20]: *Missione Iraq: Riconoscimento al Generale Roberto Vannacci,* en [www.difesa.it](http://www.difesa.it) , cit. en [www.wikipedia.org](http://www.wikipedia.org)
---
**Artículo original**: Hipérbola Janus, [_Patriots_](https://www.hiperbolajanus.com/posts/patriots-mutti/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/patriots-mutti/), 9/Ene/2025
-

@ fe02e8ec:f07fbe0b
2025-03-31 14:43:22
\
Und genau dafür wirst auch du gedrillt werden: Menschen zu jagen und töten. Unbekannte, die auch nicht wissen, was sie hier tun. Oder Unschuldige, die nicht rechtzeitig fliehen konnten. Einfach töten. Alle. Ohne zu fragen. Denn das ist deine Aufgabe, Soldat: **Töte Menschen!**
Egal, was du vorher warst, Heizungsmonteur, KFZ-Mechaniker, Veganer, Marketing-Manager, Friseur, Verkäufer, Kindergärtner: Es ist egal. Jetzt musst du töten. Denn du hast mitgemacht. Entweder, weil du es nicht ernst genommen hast, weil du dich nie für Politik interessiert hast. Oder weil du gedacht hast, das alles betrifft dich nicht. Weil du gedacht hast, Wahlen könnten etwas verändern. Oder weil du immer das Maul gehalten hast, damit dich keiner als «Rechter» bezeichnet. Egal. Jetzt musst du töten. Das ist das Spiel.
Ja, es ist ein Spiel. Grausam, abartig, menschenverachtend. Dennoch hat es Regeln: Diejenigen, die das Spiel beginnen, müssen niemals selbst auf das Schlachtfeld. Das ist die erste Regel. Ihre Söhne auch nicht, nicht die Söhne der anderen Politiker, nicht die der EU-Abgeordneten, nicht die der Parteibonzen. Auch nicht die der Banker, der Vorstandsvorsitzenden, der Chefredakteure. Denn alle wissen, wie man das Spiel spielt. Nur du nicht.
Du bist einfach eine Figur auf dem Spielfeld, die es verpasst hat, **NEIN zu sagen, als noch Gelegenheit war.** Jetzt bist du verwandelt worden in eine menschliche Drohne. Wenn sie sagen: töte!, dann tötest du. Denken kannst du, wenn alles vorbei ist. Falls du je wieder nach Hause kommst. Vielleicht sogar mit beiden Beinen und beiden Armen. Vielleicht auch nicht. Egal. Wer hätte Mitleid mit einer Spielfigur?
Nein, du musst töten. Das ist deine Aufgabe. Sie sagen es nun schon seit Monaten, warum glaubst du es nicht? Sie meinen es ernst. Wenn du den Brief in Händen hältst ist es zu spät. Es gilt dann das Notstandsrecht und keiner kann mehr verweigern. Da hättest du dich vorher drum kümmern müssen. Oder auf eine Demo gehen. Oder laut und mit klarer Stimme in jedem Gespräch den Wahnsinn anprangern. Hast du aber nicht.
**Jetzt musst du töten oder du wirst getötet.** Das ist das Spiel. Du hättest selbst denken können. Hast du aber nicht. Hast deine Zeit mit sinnlosen Videos vertan, Netflix geguckt und hast Influencerinnen geliked. Die müssen nicht an die Front. Aber du. Morgen, wenn du aufstehst, die Uniform anziehst und rausgehst, dann wirst du Befehle ausführen oder erschossen werden. Also wirst du Menschen töten. Dein Leben wird nie wieder so sein, wie zuvor. **Dein Schmerz, deine Schuld, dein Leid**: sie gehen ein in die unendliche Reihe der Soldaten, die seit Jahrhunderten dasselbe Schicksal erlitten. Deren Schreie noch immer durch den ewigen Raum hallen. Deren Opfer von den Herren des Spiels mit einem Lächeln entgegengenommen wurde. Deren Gliedmaßen auf den Schlachtfeldern liegen geblieben waren. Zum Dank erhielten sie eine Medaille. Ein Stück Blech für den rechten Arm, einen Grabstein für den Vater, den Bruder, den Sohn. Für das Vaterland. Für Europa. Für die Demokratie. Der Hohn tropft aus jedem Politikerwort, doch **die Menschen glauben noch immer die uralte Geschichte von Freund und Feind, von Gut und Böse**.
")
\
**Wer nicht aufwachen will muss töten.** Du. Nicht am Bildschirm. In der echten Welt. Wo man nicht auf Replay drücken kann. Wo man den Gegner nicht nach links oder rechts swipen kann, denn er ist echt, real, lebendig. Noch. Entweder er oder du. Jetzt ist es zu spät für Entscheidungen. Kannst du es spüren? Die Work-Life Balance wird zur Kill-or-be-Killed balance. Es gibt kein Entrinnen. Denn du hast mitgemacht. Schweigen ist Zustimmung. Sich-nicht-drumkümmern ist Zustimmung. Kriegsparteien zu wählen ist noch mehr Zustimmung.
**Heute.**
**Heute lässt sich noch etwas ändern.**
Es hat nichts zu tun mit rechts oder links. Nur mit Menschlichkeit versus Hass, Macht und dem ganz großen Geld. Das sind die Gründe, für die du töten oder sterben musst.
**Wie entscheidest du dich?**
-

@ 0d1702d6:8f1ac66f
2025-03-31 10:45:57
*Als Verrücktheit bezeichnen* \
*wir die chronische Entwicklung* \
*eines dauernden Wahnsystems* \
*bei vollkommener Erhaltung* \
*der Besonnenheit.*
**Psychiater Emil Kraepelin 1893**
Es ist **Teil des westlichen Wahnsystems** anzunehmen, Russland habe aus imperialen Absichten heraus 2022 mit nur 130.000 Soldaten die Grenze zur Ukraine überschritten, um so die gesamte Ukraine und später wohlmöglich Westeuropa militärisch einzunehmen, wie z.B. der deutsche Kriegsminister Pistorius seit 2023 suggerierte.
Nachdem die USA bereits 2014 die berechtigten Anti-Korruptions-Proteste der Ukrainer auf dem Maidan durch massive Unterstützung für einen illegalen Putsch gegen die russlandfreundliche Regierung im Sinne des von den USA gewünschten Regimewechsels manipuliert hatten, rüsteten sie in den folgenden Jahren die Ukraine massiv auf, trainierten ihre Soldaten, bauten mehr als einen Stützpunkt und machten die zwischen Ost & West hin- und hergerissene Ukraine so zielgerichtet unterhalb offizieller NATO-Mitgliedschaft schon zu einem kampfstarken eng befreundeten Partner, dessen Krieg gegen seine eigene russisch-stämmige Bevölkerung im rohstoffreichen Donbass die NATO unter Führung der USA somit auch direkt und indirekt unterstützte.
Nachdem der Westen den Russen bei der Wiedervereinigung Deutschlands versprochen hatte, die NATO keinen Zentimeter nach Osten vorzuschieben und stattdessen ein gemeinsames europäisches Sicherheits-System unter Einbeziehung Russlands gemeinsam zu entwickeln, brachen wir diese Zusicherung mit den NATO-Osterweiterungen ab 1999 mehrfach bis heute.
Russland zeigte sich bei seiner zunehmenden Umzingelung durch NATO-Staaten wesentlich nachsichtiger als es umgekehrt die USA schon bei russischen wenigen Raketen auf Kuba 1962 jemals waren und heute sein würden!
Zugleich hatte Russland seit Beginn der NATO-Osterweiterung immer unmissverständlich klar gemacht, dass es eine Stationierung von NATO-Truppen & Raketen in der Ukraine niemals tolerieren würde. Der damalige US-Senator und 2022 US-Präsident Biden sagte schon Ende der 90'er Jahre öffentlich, man werde auf diesen Wunsch der – nach Meinung von US-Geostrategen viel zu schwächen – Russen keine Rücksicht nehmen und erwarte, dass ihnen irgendwann die Nerven ob dieser provokativen Umzingelung durchgingen…
Folgerichtig simulierten die USA und die Europäer - wie Angela Merkel bereits öffentlich eingestanden - nur Verhandlungen über die Abkommen Minsk I und II, damit genügend Zeit blieb die Ukraine aufzurüsten und diese dann einen starken militärischen Schlag gegen die russisch stämmige Bevölkerung im Donbass und die russischen Soldaten auf der Krim ausführen konnte, ein Szenario, welches Anfang 2022 durch einen Truppenaufmarsch auch auf ukrainischer Seite weit fortgeschritten vorbereitet war, bevor im Februar 2022 die russische Armee die Grenze zur Ukraine überschritt.\
\
Trotz alledem kamen schon im April 2022 Unterhändler der Ukraine und Russlands in Ankara zur Übereinkunft eines Waffenstillstandes und Friedensplans (!), der dann allerdings von dem damaligen britischen Premierminister Boris Johnson – in Kooperation mit Joe Biden – durch einen Besuch in Kiew mit dem Versprechen von grenzenlosen Waffenlieferungen \
& logistischer Unterstützung durch die USA und Westeuropa „abgetrieben“ wurde.\
\
Zunächst wurden diese Tatsachen wie üblich öffentlich in deutschen und europäischen Medien als „Verschwörungstheorie“ diffamiert, bis sie in den folgenden Monaten jedoch langsam selbst in die Mainstream-Medien Deutschlands, Europas wie den USA einsickerten.\
\
**Zwischenfazit:**\
Nachdem die USA ihre so und so viel gewählte globale „Regime Change“ Operation auf dem Maidan schon 10 Jahre lang vorbereitet hatten, gelang ihnen im Jahr 2014 tatsächlich zunächst einen pro-westlichen illegalen Putschpräsidenten, danach auch weitere pro-westliche Präsidenten zu installieren und einem Teil der Weltöffentlichkeit, vor allem aber ihren „Freunden“ im Westen einzureden, die „bösen Russen“ hätten diesen Krieg quasi aus dem Nichts heraus (ohne lange Vorgeschichte!) und trotz Verhandlungen (welche realen statt nur simulierten Verhandlungen?) vom Zaun gebrochen...\
\
Damit war ihr seit über 30 Jahren offen formuliertes geostrategisches Kalkül, \
die Schwäche der Russen nach Auflösung des Warschauer Paktes auszunutzen, sie mit der NATO zu umzingeln und bei Widerstand dann eben in einem kräftezehrenden Krieg stark zu schwächen und damit ein für alle Male als ökonomische Konkurrenten in Europa auszuschalten scheinbar aufgegangen...\
\
Das paranoide alte und zugleich kindliche „Freund/Feind Schema“ hatte seinen Dienst verrichtet und das „imperiale Böse“ konnte bequem auf „Putin und die Russen“ projiziert werden. 
\
**Schizophren** ist dies auch deswegen, weil mit zweierlei Maß gemessen wurde und wird, denn niemals würden die USA auch nur eine russische Rakete auf Kuba tolerieren und gehen selber - ganz anders als Russland - global weit über die eigene Grenzsicherung hinaus, indem sie sich anmaßen, den gesamten Globus mit fast 800 Militärbasen zu überziehen und je nach Bedarf Kriege zu führen, wenn es ihnen zur Sicherung ihrer Rohstoffe - für auch unseren westlichen Lebensstil - und/oder geostrategischen Macht opportun und machbar erscheint.\
\
Deutschland spielt seit 2022 die naive und mehr als traurige Vorreiterrolle eines unterwürfigen Vasallen der so tut, als würde unsere Freiheit durch gegenseitigen Mord und Totschlag von Hunderttausenden junger Ukrainer und Russen in der Ukraine verteidigt, eine äußerst perverse und dümmliche Vorstellung ohne historische geschweige denn geo-strategische Kenntnisse und Erfahrungswerte.\
\
Demgegenüber ist klar: Es gibt nur EINE Sicherheit in Europa für alle vom Atlantik bis hinter den Ural, oder es gibt KEINE Sicherheit für Niemanden, \
wenn wir nicht die berechtigten Sicherheitsinteressen der Russen ernst nehmen, die wir, d.h. die unsere Väter und Großväter bereits im 20.Jahrhundert rücksichtslos überfallen, mit Krieg überzogen und ermordet haben.\
\
John F. Kennedy und Nikita S. Chruschtschow waren 1962 im historischen Gegenstück zum „Ukrainekrieg“, der „Kubakrise“, weise genug einen Weltkrieg durch gegenseitige Zugeständnisse zu verhindern.
**Wo sind die Politiker von Format, die in ihre Fußstapfen treten?**\
\
Es wäre eine bitterböse Farce, wenn ausgerechnet ein autoritärer Oligarchen-Präsident wie Donald Trump die Weisheit hätte, diesen Schritt zu tun...\
\
Zugleich wäre die öffentliche Bankrott-Erklärung aller europäischen Politiker, \
die sich als viel demokratischer, sachlicher und menschlicher ansehen \
und ihre eigene dramatische Fehlleistung wohl niemals eingestehen...\
\
Allein die politische wie mediale Empörungswelle in Deutschland, als Trump und Putin ganz offenlegten, wer denn in diesem Krieg das Sagen hat, \
lässt Schlimmstes befürchten. Obwohl aus gut unterrichteten Diplomatenkreisen längst durchgesickert ist, dass im Prinzip die gesamte Analyse hier unter Diplomaten anerkannt und ziemlich nah an den Tatsachen ist, gehört nicht viel Lebenserfahrung dazu zu wissen, dass die meisten der ach so mächtigen westeuropäischen Politiker dies nie zugeben werden...
-

@ 7d33ba57:1b82db35
2025-03-31 09:28:36
Rovinj is one of Croatia’s most beautiful coastal towns, known for its colorful Venetian-style buildings, cobblestone streets, and breathtaking sea views. Located on the Istrian Peninsula, Rovinj offers a mix of history, culture, and stunning beaches, making it a perfect getaway for travelers seeking both relaxation and adventure.

## **🌊 Top Things to See & Do in Rovinj**
### **1️⃣ Explore Rovinj Old Town 🏡**
- Wander through **narrow, winding streets** filled with **art galleries, boutique shops, and charming cafés**.
- Discover **Balbi’s Arch**, the old entrance to the city, and the **Clock Tower**.
- Enjoy **stunning sunset views** from the harbor.
### **2️⃣ Visit St. Euphemia’s Church ⛪**
- The **most famous landmark in Rovinj**, located at the highest point of the Old Town.
- Climb the **bell tower** for a **panoramic view** of the Adriatic and nearby islands.
- Learn about **Saint Euphemia**, the town’s patron saint, and her fascinating legend.

### **3️⃣ Relax at Rovinj’s Best Beaches 🏖️**
- **Lone Bay Beach** – A popular spot near Zlatni Rt forest, great for swimming.
- **Mulini Beach** – A stylish beach with a cocktail bar and clear waters.
- **Cuvi Beach** – A quieter, family-friendly pebble beach.
### **4️⃣ Walk or Cycle Through Golden Cape Forest Park (Zlatni Rt) 🌿🚲**
- A **protected nature park** with pine forests, walking trails, and hidden coves.
- Great for **hiking, cycling, and rock climbing**.
- Perfect for a **picnic with sea views**.
### **5️⃣ Take a Boat Trip to Rovinj Archipelago 🛥️**
- Explore **Red Island (Crveni Otok)** – A peaceful getaway with sandy beaches.
- Visit **St. Andrew’s Island**, home to a former Benedictine monastery.
- Sunset **dolphin-watching tours** are a must! 🐬

### **6️⃣ Try Authentic Istrian Cuisine 🍽️**
- **Fuži with truffles** – A local pasta dish with **Istria’s famous truffles**.
- **Istrian seafood platter** – Fresh fish, mussels, and Adriatic shrimp.
- **Olive oil & wine tasting** – Try local **Malvazija (white) and Teran (red) wines**.
### **7️⃣ Visit the Batana House Museum ⛵**
- A **unique museum dedicated to Rovinj’s traditional wooden fishing boats (batanas)**.
- Learn about **local fishing traditions and maritime culture**.
- End the visit with a traditional **batana boat ride at sunset**.

## **🚗 How to Get to Rovinj**
✈️ **By Air:** The nearest airport is **Pula Airport (PUY), 40 km away**.
🚘 **By Car:**
- **From Pula:** ~40 min (40 km)
- **From Zagreb:** ~3 hours (250 km)
- **From Ljubljana (Slovenia):** ~2.5 hours (170 km)
🚌 **By Bus:** Direct buses from **Pula, Rijeka, and Zagreb**.
🚢 **By Ferry:** Seasonal ferries connect Rovinj with **Venice, Italy** (~2.5 hours).

## **💡 Tips for Visiting Rovinj**
✅ **Best time to visit?** **May–September** for warm weather & festivals ☀️
✅ **Wear comfy shoes** – The Old Town streets are made of polished stone & can be slippery 👟
✅ **Book restaurants in advance** – Rovinj is a foodie hotspot, especially in summer 🍷
✅ **Take a sunset walk along the harbor** – One of the most romantic views in Croatia 🌅
✅ **Bring cash** – Some smaller shops and taverns still prefer cash 💶

-

@ 78c90fc4:4bff983c
2025-03-31 08:13:17
Die Operation „Cast Thy Bread“ war eine verdeckte Kampagne zur biologischen Kriegsführung, die von der Haganah und später von den israelischen Verteidigungsstreitkräften während des arabisch-israelischen Krieges 1948 durchgeführt wurde\[1]\[3]. Bei der Operation, die im April 1948 begann, wurden Trinkwasserquellen mit Typhusbakterien verseucht, um palästinensisch-arabische Zivilisten und verbündete arabische Armeen anzugreifen\[1]\[3].
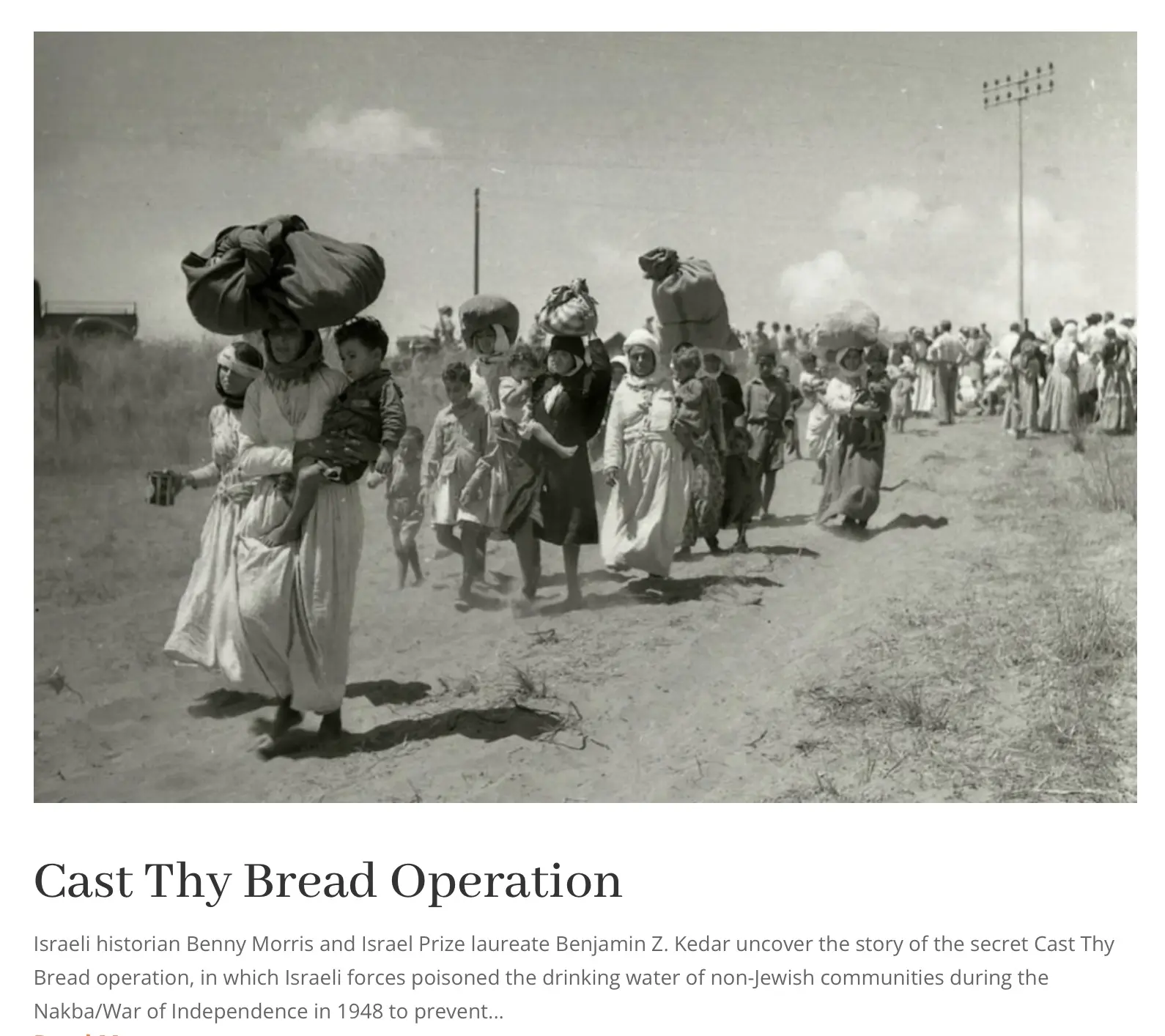
\
\
\## Wichtige Details\
\
\- \*\*Ziel\*\*: Palästinensische Araber an der Rückkehr in eroberte Dörfer zu hindern und die Versuche der arabischen Armeen, Gebiete zurückzuerobern, zu behindern\[1].\
\- \*\*Methoden\*\*: Israelische Streitkräfte setzten Typhuskeime in Flaschen, Reagenzgläsern und Thermoskannen ein, um Brunnen und Wasservorräte in palästinensischen Gebieten zu vergiften\[1]\[3].\
\- \*\*Führung\*\*: Die Operation wurde vom israelischen Premierminister David Ben-Gurion und dem Generalstabschef der IDF, Yigael Yadin, beaufsichtigt und genehmigt\[1].\
\
\## Bemerkenswerte Vorfälle\
\
\- Akkon (Akka)\*\*: Die Wasserversorgung der Stadt wurde am 15. Mai 1948 verseucht, was zu einer Typhusepidemie und „extremer Verzweiflung“ unter den Einwohnern führte\[1]\[3].\
\- \*\*Gaza\*\*: Im Mai 1948 versuchten vier Soldaten der israelischen Spezialeinheiten, die örtliche Wasserversorgung zu vergiften, wurden jedoch gefangen genommen und hingerichtet\[1].\
\- \*\*Andere Orte\*\*: Auch in Jericho, Eilabun und palästinensischen Vierteln in Jerusalem wurden Brunnen vergiftet\[1]\[3].\
\
\## Folgen\
\
Die Operation führte zu schweren Erkrankungen unter den palästinensischen Anwohnern, von denen Dutzende betroffen sein sollen\[1]\[3]. Sie erzielte jedoch nicht die von ihren Befürwortern erhoffte lähmende Wirkung und wurde im Dezember 1948 eingestellt\[1].\
\
\## Historische Bedeutung\
\
Die Operation „Gegossenes Brot“ wurde als Kriegsverbrechen und als Akt der ethnischen Säuberung eingestuft\[1]. Ihre Enthüllung hat eine Kontroverse und Debatte über die im Krieg von 1948 angewandten Taktiken und ihre langfristigen Auswirkungen auf den israelisch-palästinensischen Konflikt ausgelöst\[2]\[4].
Quellen
\[1] Operation Cast Thy Bread - Wikipedia https\://en.wikipedia.org/wiki/Operation\_Cast\_Thy\_Bread
\[2] Cast Thy Bread Archives - Promised Land Museum https\://promisedlandmuseum.org/tag/cast-thy-bread/
\[3] From 'Virtuous Boy' to Murderous Fanatic: David Ben-Gurion and the ... https\://www\.euppublishing.com/doi/10.3366/hlps.2023.0308
\[4] Historians reveal Israel's use of poison against Palestinians https\://www\.middleeastmonitor.com/20221011-historians-reveal-israels-use-of-poison-against-palestinians/
\[5] Thoughts on Operation Cast Thy Bread? : r/IsraelPalestine - Reddit https\://www\.reddit.com/r/IsraelPalestine/comments/1g02b64/thoughts\_on\_operation\_cast\_thy\_bread/
\[6] 'Cast thy bread': Israeli biological warfare during the 1948 War https\://www\.tandfonline.com/doi/abs/10.1080/00263206.2022.2122448
\[7] 'Cast thy bread': Israeli biological warfare during the 1948 War https\://cris.bgu.ac.il/en/publications/cast-thy-bread-israeli-biological-warfare-during-the-1948-war
\[8] 'Cast thy bread': Israeli biological warfare during the 1948 War https\://www\.tandfonline.com/doi/full/10.1080/00263206.2022.2122448
\
Artikel <https://x.com/RealWsiegrist/status/1906616394747179136>
Nakba
<https://waltisiegrist.locals.com/upost/2033124/die-siedler-fordern-ganz-offen-eine-zweite-nakba>
-

@ 0fa80bd3:ea7325de
2025-01-29 14:44:48
![[yedinaya-rossiya-bear.png]]
1️⃣ Be where the bear roams. Stay in its territory, where it hunts for food. No point setting a trap in your backyard if the bear’s chilling in the forest.
2️⃣ Set a well-hidden trap. Bury it, disguise it, and place the bait right in the center. Bears are omnivores—just like secret police KGB agents. And what’s the tastiest bait for them? Money.
3️⃣ Wait for the bear to take the bait. When it reaches in, the trap will snap shut around its paw. It’ll be alive, but stuck. No escape.
Now, what you do with a trapped bear is another question... 😏
-

@ c631e267:c2b78d3e
2025-03-31 07:23:05
*Der Irrsinn ist bei Einzelnen etwas Seltenes –* *\
aber bei Gruppen, Parteien, Völkern, Zeiten die Regel.* *\
Friedrich Nietzsche*  
**Erinnern Sie sich an die Horrorkomödie «Scary Movie»?** Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?

**Diese Szene kommt mir automatisch in den Sinn,** wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real.
**Die Europäische Union hat sich selbst über Jahre** konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt.
**In den USA haben sich die Vorzeichen allerdings mittlerweile geändert,** und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen.
**Statt jedoch umzukehren oder wenigstens zu bremsen** und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die [Kommentatoren](https://transition-news.org/wird-ihr-stahlhelm-schon-gegossen) des Events gegenseitig in sensationslüsterner «Berichterstattung».
**Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen,** Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, [selbstzerstörerischen](https://transition-news.org/okonomen-eu-rustet-auf-und-schiesst-sich-selbst-ins-knie) Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», [erklärte](https://ec.europa.eu/commission/presscorner/detail/de/ip_25_793) die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte.
**Zusätzlich brisant ist, dass aktuell «die ganze EU** **[von Deutschen regiert](https://transition-news.org/die-ganze-eu-wird-von-deutschen-regiert)** **wird»,** wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen.
**Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung** hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen.
**Es wird dringend Zeit, dass wir, der Souverän,** diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts [den Frieden auszurufen](https://transition-news.org/ein-zeichen-fur-die-friedliche-zukunft-europas-setzen). Seien wir dabei!
*\[Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/vertical-abstract-concept-car-8992833/)]*
***
Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/mit-vollgas-in-die-sackgasse)*** erschienen.
-

@ 0fa80bd3:ea7325de
2025-01-29 05:55:02
The land that belongs to the indigenous peoples of Russia has been seized by a gang of killers who have unleashed a war of extermination. They wipe out anyone who refuses to conform to their rules. Those who disagree and stay behind are tortured and killed in prisons and labor camps. Those who flee lose their homeland, dissolve into foreign cultures, and fade away. And those who stand up to protect their people are attacked by the misled and deceived. The deceived die for the unchecked greed of a single dictator—thousands from both sides, people who just wanted to live, raise their kids, and build a future.
Now, they are forced to make an impossible choice: abandon their homeland or die. Some perish on the battlefield, others lose themselves in exile, stripped of their identity, scattered in a world that isn’t theirs.
There’s been endless debate about how to fix this, how to clear the field of the weeds that choke out every new sprout, every attempt at change. But the real problem? We can’t play by their rules. We can’t speak their language or use their weapons. We stand for humanity, and no matter how righteous our cause, we will not multiply suffering. Victory doesn’t come from matching the enemy—it comes from staying ahead, from using tools they haven’t mastered yet. That’s how wars are won.
Our only resource is the **will of the people** to rewrite the order of things. Historian Timothy Snyder once said that a nation cannot exist without a city. A city is where the most active part of a nation thrives. But the cities are occupied. The streets are watched. Gatherings are impossible. They control the money. They control the mail. They control the media. And any dissent is crushed before it can take root.
So I started asking myself: **How do we stop this fragmentation?** How do we create a space where people can **rebuild their connections** when they’re ready? How do we build a **self-sustaining network**, where everyone contributes and benefits proportionally, while keeping their freedom to leave intact? And more importantly—**how do we make it spread, even in occupied territory?**
In 2009, something historic happened: **the internet got its own money.** Thanks to **Satoshi Nakamoto**, the world took a massive leap forward. Bitcoin and decentralized ledgers shattered the idea that money must be controlled by the state. Now, to move or store value, all you need is an address and a key. A tiny string of text, easy to carry, impossible to seize.
That was the year money broke free. The state lost its grip. Its biggest weapon—physical currency—became irrelevant. Money became **purely digital.**
The internet was already **a sanctuary for information**, a place where people could connect and organize. But with Bitcoin, it evolved. Now, **value itself** could flow freely, beyond the reach of authorities.
Think about it: when seedlings are grown in controlled environments before being planted outside, they **get stronger, survive longer, and bear fruit faster.** That’s how we handle crops in harsh climates—nurture them until they’re ready for the wild.
Now, picture the internet as that **controlled environment** for **ideas**. Bitcoin? It’s the **fertile soil** that lets them grow. A testing ground for new models of interaction, where concepts can take root before they move into the real world. If **nation-states are a battlefield, locked in a brutal war for territory, the internet is boundless.** It can absorb any number of ideas, any number of people, and it doesn’t **run out of space.**
But for this ecosystem to thrive, people need safe ways to communicate, to share ideas, to build something real—**without surveillance, without censorship, without the constant fear of being erased.**
This is where **Nostr** comes in.
Nostr—"Notes and Other Stuff Transmitted by Relays"—is more than just a messaging protocol. **It’s a new kind of city.** One that **no dictator can seize**, no corporation can own, no government can shut down.
It’s built on **decentralization, encryption, and individual control.** Messages don’t pass through central servers—they are relayed through independent nodes, and users choose which ones to trust. There’s no master switch to shut it all down. Every person owns their identity, their data, their connections. And no one—no state, no tech giant, no algorithm—can silence them.
In a world where cities fall and governments fail, **Nostr is a city that cannot be occupied.** A place for ideas, for networks, for freedom. A city that grows stronger **the more people build within it**.
-

@ 9e69e420:d12360c2
2025-01-26 15:26:44
Secretary of State Marco Rubio issued new guidance halting spending on most foreign aid grants for 90 days, including military assistance to Ukraine. This immediate order shocked State Department officials and mandates “stop-work orders” on nearly all existing foreign assistance awards.
While it allows exceptions for military financing to Egypt and Israel, as well as emergency food assistance, it restricts aid to key allies like Ukraine, Jordan, and Taiwan. The guidance raises potential liability risks for the government due to unfulfilled contracts.
A report will be prepared within 85 days to recommend which programs to continue or discontinue.
-

@ 78c90fc4:4bff983c
2025-03-31 07:03:41
In Palästina und im Ausland wurde das Abkommen einzelner jüdischer Organisationen mit dem [nationalsozialistischen Deutschland](https://de.m.wikipedia.org/wiki/Deutsches_Reich_1933_bis_1945) heftig kritisiert. Auf dem 18. [Zionistenkongress](https://de.m.wikipedia.org/wiki/Zionistenkongress) 1933 in Prag etwa bezeichnete der Schriftsteller [Schalom Asch](https://de.m.wikipedia.org/wiki/Schalom_Asch) das Abkommen mit [Hitlers Regime](https://de.m.wikipedia.org/wiki/NS-Regime) als „Verrat am Weltjudentum“. [Chaim Arlosoroff](https://de.m.wikipedia.org/wiki/Chaim_Arlosoroff), der damalige Verhandlungsführer der Jewish Agency, wurde wahrscheinlich deshalb im Juni 1933 Opfer [eines Mordanschlags](https://de.m.wikipedia.org/wiki/Chaim_Arlosoroff#Ermordung).
 
https\://de.m.wikipedia.org/wiki/Ha’avara-Abkommen
Am 16. Juni 1933 wurde Chaim Arlosoroff kurz nach seiner Rückkehr von den Transfer-Verhandlungen in Deutschland durch den Pistolenschuss eines Attentäters schwer verletzt, als er mit seiner Frau Sima, geb. Rubin, am Strand von Tel Aviv entlangging. Er verstarb am folgenden Tag im Krankenhaus. Wer der Attentäter war, ist bis heute ungeklärt. Zunächst wurden drei Verdächtige angeklagt. Zwei von ihnen wurden freigesprochen, einer, [Abraham Stavsky](https://de.m.wikipedia.org/wiki/Abraham_Stavsky), wurde verurteilt, doch das Urteil wurde durch das oberste Appellationsgericht aufgehoben.
<https://de.m.wikipedia.org/wiki/Chaim_Arlosoroff#Ermordung>
**Instrumentalisierung des Holocaust**
Von Anneliese Fikentscher und Andreas Neumann
Zum Schluss ein Zitat aus dem 2017 erschienenen Buch "Die israelisch-jüdische Tragödie. Von Auschwitz zum Besatzungs- und Apartheidstaat. Das Ende der Verklärung" von Arn Strohmeyer: „Der vielleicht radikalste Kritiker des israelischen Holocaustgedenkens ist der amerikanisch -jüdische Politologe Norman Finkelstein. Er wendet sich vor allem gegen das in Israel und den USA verwendete Dogma, der Holocaust sei 'einzigartig' gewesen und mit anderen Verbrechen nicht vergleichbar, dass er in der Geschichte also ohne Parallele sei. Diese Behauptung – so Finkelstein – impliziert eine Reihe anderer Behauptungen, die wiederum die Instrumentalisierung des Holocaust ausmachen. Erstens: Die Konstruktion des Holocaust als einzigartig gilt als gegeben, sie zu leugnen gilt als Leugnung des Holocaust. Diese Behauptung schließt zweitens ein rationales Verständnis des Holocaust aus, er macht den Holocaust zu einem Mysterium, wie Elie Wiesel ihn verstanden hat. Einzigartiges Leid verleiht drittens einen einzigartigen Anspruch. Die Unvergleichlichkeit des Holocaust stellt also ein moralisches Kapital dar, das Israel als politisches Alibi benutzt. Israel kann – so Finkelstein – diese moralischen und emotionalen Ansprüche an andere Staaten stellen und die Anerkennung seines Rechts einfordern, dass es als besonders bedroht gelten kann und seine Anstrengungen zum Überleben der Unterstützung bedarf. Die Behauptung der Einzigartigkeit des Holocaust beinhaltet auch die Behauptung der jüdischen Einzigartigkeit. Der Holocaust ist also etwas Besonderes, weil Juden etwas Besonderes sind, was man als säkularisierte Version der Auserwähltheit deuten kann. Diese Behauptungen – so Finkelstein – sollen Israels Sonderstellung legitimieren, sollen von vornherein jede unmenschliche Behandlung von Nichtjuden entschuldigen (Israel ist 'alles erlaubt!') und machen diesen Staat und seine Politik gegen jede Kritik immun. Bei dieser Instrumentalisierung des Holocaust bleiben die Rechte und die Würde der Opfer – welcher auch immer – völlig auf der Strecke.“ Ist das einer breiten Öffentlichkeit bewusst?
<http://www.nrhz.de/flyer/beitrag.php?id=24469>
Perplexity:
Der Schriftsteller Schalom Asch kritisierte das Ha'avara-Abkommen scharf auf dem 18. Zionistischen Kongress, der vom 21. August bis 4. September 1933 in Prag stattfand. Er bezeichnete das Abkommen mit dem Hitler-Regime als "ein Verrat am Weltjudentum"\[1]\[2].
Das Ha'avara-Abkommen wurde am 10. August 1933 zwischen der Jewish Agency, der Zionistischen Vereinigung für Deutschland und dem deutschen Reichsministerium für Wirtschaft geschlossen. Es sollte die Emigration deutscher Juden nach Palästina erleichtern und gleichzeitig den deutschen Export fördern\[2].
Am 5. November 1933 wurde die "Trust and Transfer Office Ha'avara Ltd." als quasi privates Unternehmen eingetragen\[1]\[3]. Trotz der anfänglichen Kritik billigte die Zionistische Weltorganisation auf ihrer Konferenz am 20. August 1935 in Luzern mit Mehrheit den Ha'avara-Abschluss und übernahm sogar dessen gesamte Tätigkeit in eigene Regie\[1]\[2]\[3].
Das Abkommen war innerhalb der zionistischen Bewegung umstritten, da es den gleichzeitig vorangetriebenen Boykottmaßnahmen gegen die Nationalsozialisten zuwiderlief\[2]. Es ermöglichte deutschen Juden, einen Teil ihres Vermögens nach Palästina zu transferieren, wobei ein bestimmter Prozentsatz als Reichsfluchtsteuer vom deutschen Fiskus einbehalten wurde\[5].
Quellen
\[1] Zionistenkongress - Wikiwand https\://www\.wikiwand.com/de/articles/Zionistenkongress
\[2] Ha'avara-Abkommen - Wikiwand https\://www\.wikiwand.com/de/articles/Haavara-Abkommen
\[3] Zionistenkongress - Wikipedia https\://de.wikipedia.org/wiki/Zionistenkongress
\[4] Schalom Asch - Wikipedia https\://de.wikipedia.org/wiki/Schalom\_Asch
\[5] Ha'avara-Abkommen - Wikipedia https\://de.wikipedia.org/wiki/Ha%E2%80%99avara-Abkommen
\[6] Stefan Zweig. Briefe zum Judentum. Hg. v. Stefan Litt. Berlin ... https\://judaica.ch/article/view/8320/11519
\[7] Das Haavara-Transfer-Abkommen | Die Wohnung | bpb.de https\://www\.bpb.de/themen/nationalsozialismus-zweiter-weltkrieg/die-wohnung/195259/das-haavara-transfer-abkommen/
\[8] Jüdischer Verlag - Wikipedia https\://de.wikipedia.org/wiki/J%C3%BCdischer\_Verlag
Artikel <https://x.com/RealWsiegrist/status/1906601705355252211>
-

@ da0b9bc3:4e30a4a9
2025-03-31 06:32:43
Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/929968
-

@ 9e69e420:d12360c2
2025-01-26 01:31:31
## Chef's notes
# arbitray
- test
- of
- chefs notes
## hedding 2
## Details
- ⏲️ Prep time: 20
- 🍳 Cook time: 1 hour
- 🍽️ Servings: 5
## Ingredients
- Test ingredient
- 2nd test ingredient
## Directions
1. Bake
2. Cool
-

@ 9e69e420:d12360c2
2025-01-25 22:16:54
President Trump plans to withdraw 20,000 U.S. troops from Europe and expects European allies to contribute financially to the remaining military presence. Reported by ANSA, Trump aims to deliver this message to European leaders since taking office. A European diplomat noted, “the costs cannot be borne solely by American taxpayers.”
The Pentagon hasn't commented yet. Trump has previously sought lower troop levels in Europe and had ordered cuts during his first term. The U.S. currently maintains around 65,000 troops in Europe, with total forces reaching 100,000 since the Ukraine invasion. Trump's new approach may shift military focus to the Pacific amid growing concerns about China.
[Sauce](https://www.stripes.com/theaters/europe/2025-01-24/trump-europe-troop-cuts-16590074.html)
-

@ 6be5cc06:5259daf0
2025-01-21 20:58:37
A seguir, veja como instalar e configurar o **Privoxy** no **Pop!_OS**.
---
### **1. Instalar o Tor e o Privoxy**
Abra o terminal e execute:
```bash
sudo apt update
sudo apt install tor privoxy
```
**Explicação:**
- **Tor:** Roteia o tráfego pela rede Tor.
- **Privoxy:** Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
---
### **2. Configurar o Privoxy**
Abra o arquivo de configuração do Privoxy:
```bash
sudo nano /etc/privoxy/config
```
Navegue até a última linha (atalho: **`Ctrl`** + **`/`** depois **`Ctrl`** + **`V`** para navegar diretamente até a última linha) e insira:
```bash
forward-socks5 / 127.0.0.1:9050 .
```
Isso faz com que o **Privoxy** envie todo o tráfego para o **Tor** através da porta **9050**.
Salve (**`CTRL`** + **`O`** e **`Enter`**) e feche (**`CTRL`** + **`X`**) o arquivo.
---
### **3. Iniciar o Tor e o Privoxy**
Agora, inicie e habilite os serviços:
```bash
sudo systemctl start tor
sudo systemctl start privoxy
sudo systemctl enable tor
sudo systemctl enable privoxy
```
**Explicação:**
- **start:** Inicia os serviços.
- **enable:** Faz com que iniciem automaticamente ao ligar o PC.
---
### **4. Configurar o Navegador Firefox**
Para usar a rede **Tor** com o Firefox:
1. Abra o Firefox.
2. Acesse **Configurações** → **Configurar conexão**.
3. Selecione **Configuração manual de proxy**.
4. Configure assim:
- **Proxy HTTP:** `127.0.0.1`
- **Porta:** `8118` (porta padrão do **Privoxy**)
- **Domínio SOCKS (v5):** `127.0.0.1`
- **Porta:** `9050`
5. Marque a opção **"Usar este proxy também em HTTPS"**.
6. Clique em **OK**.
---
### **5. Verificar a Conexão com o Tor**
Abra o navegador e acesse:
```text
https://check.torproject.org/
```
Se aparecer a mensagem **"Congratulations. This browser is configured to use Tor."**, a configuração está correta.
---
### **Dicas Extras**
- **Privoxy** pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o **Privoxy**.
-

@ 9e69e420:d12360c2
2025-01-21 19:31:48
Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits.
## Active Compounds
The oil's therapeutic properties stem from its key bioactive components:
- Carvacrol and thymol (primary active compounds)
- Polyphenols and other antioxidant
## Antimicrobial Properties
**Bacterial Protection**
The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance.
**Antifungal Effects**
It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections.
## Digestive Health Benefits
Oregano oil supports digestive wellness by:
- Promoting gastric juice secretion and enzyme production
- Helping treat Small Intestinal Bacterial Overgrowth (SIBO)
- Managing digestive discomfort, bloating, and IBS symptoms
## Anti-inflammatory and Antioxidant Effects
The oil provides significant protective benefits through:
- Powerful antioxidant activity that fights free radicals
- Reduction of inflammatory markers in the body
- Protection against oxidative stress-related conditions
## Respiratory Support
It aids respiratory health by:
- Loosening mucus and phlegm
- Suppressing coughs and throat irritation
- Supporting overall respiratory tract function
## Additional Benefits
**Skin Health**
- Improves conditions like psoriasis, acne, and eczema
- Supports wound healing through antibacterial action
- Provides anti-aging benefits through antioxidant properties
**Cardiovascular Health**
Studies show oregano oil may help:
- Reduce LDL (bad) cholesterol levels
- Support overall heart health
**Pain Management**
The oil demonstrates effectiveness in:
- Reducing inflammation-related pain
- Managing muscle discomfort
- Providing topical pain relief
## Safety Note
While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications.
-

@ b17fccdf:b7211155
2025-01-21 17:02:21
The past 26 August, Tor [introduced officially](https://blog.torproject.org/introducing-proof-of-work-defense-for-onion-services/) a proof-of-work (PoW) defense for onion services designed to prioritize verified network traffic as a deterrent against denial of service (DoS) attacks.
~ > This feature at the moment, is [deactivate by default](https://gitlab.torproject.org/tpo/core/tor/-/blob/main/doc/man/tor.1.txt#L3117), so you need to follow these steps to activate this on a MiniBolt node:
* Make sure you have the latest version of Tor installed, at the time of writing this post, which is v0.4.8.6. Check your current version by typing
```
tor --version
```
**Example** of expected output:
```
Tor version 0.4.8.6.
This build of Tor is covered by the GNU General Public License (https://www.gnu.org/licenses/gpl-3.0.en.html)
Tor is running on Linux with Libevent 2.1.12-stable, OpenSSL 3.0.9, Zlib 1.2.13, Liblzma 5.4.1, Libzstd N/A and Glibc 2.36 as libc.
Tor compiled with GCC version 12.2.0
```
~ > If you have v0.4.8.X, you are **OK**, if not, type `sudo apt update && sudo apt upgrade` and confirm to update.
* Basic PoW support can be checked by running this command:
```
tor --list-modules
```
Expected output:
```
relay: yes
dirauth: yes
dircache: yes
pow: **yes**
```
~ > If you have `pow: yes`, you are **OK**
* Now go to the torrc file of your MiniBolt and add the parameter to enable PoW for each hidden service added
```
sudo nano /etc/tor/torrc
```
Example:
```
# Hidden Service BTC RPC Explorer
HiddenServiceDir /var/lib/tor/hidden_service_btcrpcexplorer/
HiddenServiceVersion 3
HiddenServicePoWDefensesEnabled 1
HiddenServicePort 80 127.0.0.1:3002
```
~ > Bitcoin Core and LND use the Tor control port to automatically create the hidden service, requiring no action from the user. We have submitted a feature request in the official GitHub repositories to explore the need for the integration of Tor's PoW defense into the automatic creation process of the hidden service. You can follow them at the following links:
* Bitcoin Core: https://github.com/lightningnetwork/lnd/issues/8002
* LND: https://github.com/bitcoin/bitcoin/issues/28499
---
More info:
* https://blog.torproject.org/introducing-proof-of-work-defense-for-onion-services/
* https://gitlab.torproject.org/tpo/onion-services/onion-support/-/wikis/Documentation/PoW-FAQ
---
Enjoy it MiniBolter! 💙
 @ 39cc53c9:27168656
2025-03-30 05:54:53> [Read the original blog post](https://blog.kycnot.me/p/kyc-no-thanks) Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations. Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms. ## Rights for Illusions KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks? The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors." However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% [^1] – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service. Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy. To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% [^1] of less-than-careful criminals. ## KYC? Not you. > KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. [^2] KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible. For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded. Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether. It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms. ## You're not welcome Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right? This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to. Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely. ## Your identity has been stolen KYC data has been found to be for sale on many dark net markets[^3]. Exchanges may have leaks or hacks, and such leaks contain **very** sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it? As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. [^3] In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised. ## (they) Know Your Coins You may already know that **Bitcoin and most cryptocurrencies have a transparent public blockchain**, meaning that all data is shown unencrypted for everyone to see and recorded **forever**. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced. If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with. ## Conclusions To sum up, **KYC does not protect individuals**; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred. The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies. The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable. > Edited 20/03/2024 > * Add reference to the 1% statement on [Rights for Illusions](#rights-for-illusions) section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity [^1] [^1]: https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/ [^2]: https://old.reddit.com/r/BitcoinBeginners/comments/k2bve1/is_kyc_bad_if_so_why/gdtc8kz [^3]: https://www.ccn.com/hacked-customer-data-from-world-leading-cryptocurrency-exchanges-for-sale-on-the-dark-web/
@ 39cc53c9:27168656
2025-03-30 05:54:53> [Read the original blog post](https://blog.kycnot.me/p/kyc-no-thanks) Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations. Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms. ## Rights for Illusions KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks? The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors." However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% [^1] – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service. Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy. To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% [^1] of less-than-careful criminals. ## KYC? Not you. > KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. [^2] KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible. For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded. Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether. It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms. ## You're not welcome Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right? This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to. Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely. ## Your identity has been stolen KYC data has been found to be for sale on many dark net markets[^3]. Exchanges may have leaks or hacks, and such leaks contain **very** sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it? As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. [^3] In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised. ## (they) Know Your Coins You may already know that **Bitcoin and most cryptocurrencies have a transparent public blockchain**, meaning that all data is shown unencrypted for everyone to see and recorded **forever**. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced. If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with. ## Conclusions To sum up, **KYC does not protect individuals**; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred. The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies. The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable. > Edited 20/03/2024 > * Add reference to the 1% statement on [Rights for Illusions](#rights-for-illusions) section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity [^1] [^1]: https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/ [^2]: https://old.reddit.com/r/BitcoinBeginners/comments/k2bve1/is_kyc_bad_if_so_why/gdtc8kz [^3]: https://www.ccn.com/hacked-customer-data-from-world-leading-cryptocurrency-exchanges-for-sale-on-the-dark-web/ @ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all. That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission. As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently. Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive. Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally. The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match. When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol. Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all. That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission. As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently. Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive. Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally. The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match. When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol. Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit. @ b2d670de:907f9d4a
2025-03-25 20:17:57This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users. ## Table of Contents 1. Prerequisites 2. Initial Server Setup 3. Installing Strfry Nostr Relay 4. Configuring Your Relay 5. Setting Up TOR 6. Making Your Relay Available on TOR 7. Testing Your Setup] 8. Maintenance and Security 9. Troubleshooting ## Prerequisites - A Debian or Ubuntu server - Basic familiarity with command line operations (most steps are explained in detail) - Root or sudo access to your server ## Initial Server Setup First, let's make sure your server is properly set up and secured. ### Update Your System Connect to your server via SSH and update your system: ```bash sudo apt update sudo apt upgrade -y ``` ### Set Up a Basic Firewall Install and configure a basic firewall: ```bash sudo apt install ufw -y sudo ufw allow ssh sudo ufw enable ``` This allows SSH connections while blocking other ports for security. ## Installing Strfry Nostr Relay This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the `DEPLOYMENT.md` document in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps [here](https://github.com/hoytech/strfry/blob/master/docs/DEPLOYMENT.md). ### Install Dependencies First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry: ```bash sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-dev ``` Here's why each dependency is needed: **Basic Development Tools:** - `git`: Version control system used to clone the Strfry repository and manage code updates - `build-essential`: Meta-package that includes compilers (gcc, g++), make, and other essential build tools **Perl Dependencies** (used for Strfry's build scripts): - `libyaml-perl`: Perl interface to parse YAML configuration files - `libtemplate-perl`: Template processing system used during the build process - `libregexp-grammars-perl`: Advanced regular expression handling for Perl scripts **Core Libraries for Strfry:** - `libssl-dev`: Development files for OpenSSL, used for secure connections and cryptographic operations - `zlib1g-dev`: Compression library that Strfry uses to reduce data size - `liblmdb-dev`: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend - `libflatbuffers-dev`: Memory-efficient serialization library for structured data - `libsecp256k1-dev`: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures - `libzstd-dev`: Fast real-time compression algorithm for efficient data storage and transmission ### Clone and Build Strfry Clone the Strfry repository: ```bash git clone https://github.com/hoytech/strfry.git cd strfry ``` Build Strfry: ```bash git submodule update --init make setup-golpe make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores) ``` This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime. ### Install Strfry Install the Strfry binary to your system path: ```bash sudo cp strfry /usr/local/bin ``` This makes the `strfry` command available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions. ## Configuring Your Relay ### Create Strfry User Create a dedicated user for running Strfry. This enhances security by isolating the relay process: ```bash sudo useradd -M -s /usr/sbin/nologin strfry ``` The `-M` flag prevents creating a home directory, and `-s /usr/sbin/nologin` prevents anyone from logging in as this user. This is a security best practice for service accounts. ### Create Data Directory Create a directory for Strfry's data: ```bash sudo mkdir /var/lib/strfry sudo chown strfry:strfry /var/lib/strfry sudo chmod 755 /var/lib/strfry ``` This creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it. ### Configure Strfry Copy the sample configuration file: ```bash sudo cp strfry.conf /etc/strfry.conf ``` Edit the configuration file: ```bash sudo nano /etc/strfry.conf ``` Modify the database path: ``` # Find this line: db = "./strfry-db/" # Change it to: db = "/var/lib/strfry/" ``` Check your system's hard limit for file descriptors: ```bash ulimit -Hn ``` Update the `nofiles` setting in your configuration to match this value (or set to 0): ``` # Add or modify this line in the config (example if your limit is 524288): nofiles = 524288 ``` The `nofiles` setting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular. You might also want to customize your relay's information in the config file. Look for the `info` section and update it with your relay's name, description, and other details. Set ownership of the configuration file: ```bash sudo chown strfry:strfry /etc/strfry.conf ``` ### Create Systemd Service Create a systemd service file for managing Strfry: ```bash sudo nano /etc/systemd/system/strfry.service ``` Add the following content: ```ini [Unit] Description=strfry relay service [Service] User=strfry ExecStart=/usr/local/bin/strfry relay Restart=on-failure RestartSec=5 ProtectHome=yes NoNewPrivileges=yes ProtectSystem=full LimitCORE=1000000000 [Install] WantedBy=multi-user.target ``` This systemd service configuration: - Runs Strfry as the dedicated strfry user - Automatically restarts the service if it fails - Implements security measures like `ProtectHome` and `NoNewPrivileges` - Sets resource limits appropriate for a relay Enable and start the service: ```bash sudo systemctl enable strfry.service sudo systemctl start strfry ``` Check the service status: ```bash sudo systemctl status strfry ``` ### Verify Relay is Running Test that your relay is running locally: ```bash curl localhost:7777 ``` You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR. ## Setting Up TOR Now let's make your relay accessible as a TOR hidden service. ### Install TOR Install TOR from the package repositories: ```bash sudo apt install -y tor ``` This installs the TOR daemon that will create and manage your hidden service. ### Configure TOR Edit the TOR configuration file: ```bash sudo nano /etc/tor/torrc ``` Scroll down to wherever you see a commented out part like this: ``` #HiddenServiceDir /var/lib/tor/hidden_service/ #HiddenServicePort 80 127.0.0.1:80 ``` Under those lines, add the following lines to set up a hidden service for your relay: ``` HiddenServiceDir /var/lib/tor/strfry-relay/ HiddenServicePort 80 127.0.0.1:7777 ``` This configuration: - Creates a hidden service directory at `/var/lib/tor/strfry-relay/` - Maps port 80 on your .onion address to port 7777 on your local machine - Keeps all traffic encrypted within the TOR network Create the directory for your hidden service: ```bash sudo mkdir -p /var/lib/tor/strfry-relay/ sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/ sudo chmod 700 /var/lib/tor/strfry-relay/ ``` The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys. Restart TOR to apply changes: ```bash sudo systemctl restart tor ``` ## Making Your Relay Available on TOR ### Get Your Onion Address After restarting TOR, you can find your onion address: ```bash sudo cat /var/lib/tor/strfry-relay/hostname ``` This will output something like `abcdefghijklmnopqrstuvwxyz234567.onion`, which is your relay's unique .onion address. This is what you'll share with others to access your relay. ### Understanding Onion Addresses The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key. Your users will need to use this address with the WebSocket protocol prefix to connect: `ws://youronionaddress.onion` ## Testing Your Setup ### Test with a Nostr Client The best way to test your relay is with an actual Nostr client that supports TOR: 1. Open your TOR browser 2. Go to your favorite client, either on clearnet or an onion service. - Check out [this list](https://github.com/0xtrr/onion-service-nostr-clients?tab=readme-ov-file#onion-service-nostr-clients) of nostr clients available over TOR. 3. Add your relay URL: `ws://youronionaddress.onion` to your relay list 4. Try posting a note and see if it appears on your relay - In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay. - Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected. Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too). ## Maintenance and Security ### Regular Updates Keep your system, TOR, and relay updated: ```bash # Update system sudo apt update sudo apt upgrade -y # Update Strfry cd ~/strfry git pull git submodule update make -j2 sudo cp strfry /usr/local/bin sudo systemctl restart strfry # Verify TOR is still running properly sudo systemctl status tor ``` Regular updates are crucial for security, especially for TOR which may have security-critical updates. ### Database Management Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups. ### Monitoring Logs To monitor your Strfry logs: ```bash sudo journalctl -u strfry -f ``` To check TOR logs: ```bash sudo journalctl -u tor -f ``` Monitoring logs helps you identify potential issues and understand how your relay is being used. ### Backup This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server. ```bash # Stop the relay temporarily sudo systemctl stop strfry # Backup the database sudo cp -r /var/lib/strfry /path/to/backup/location # Restart the relay sudo systemctl start strfry ``` Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it. ```bash sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/location ``` ## Troubleshooting ### Relay Not Starting If your relay doesn't start: ```bash # Check logs sudo journalctl -u strfry -e # Verify configuration cat /etc/strfry.conf # Check permissions ls -la /var/lib/strfry ``` Common issues include: - Incorrect configuration format - Permission problems with the data directory - Port already in use (another service using port 7777) - Issues with setting the nofiles limit (setting it too big) ### TOR Hidden Service Not Working If your TOR hidden service is not accessible: ```bash # Check TOR logs sudo journalctl -u tor -e # Verify TOR is running sudo systemctl status tor # Check onion address sudo cat /var/lib/tor/strfry-relay/hostname # Verify TOR configuration sudo cat /etc/tor/torrc ``` Common TOR issues include: - Incorrect directory permissions - TOR service not running - Incorrect port mapping in torrc ### Testing Connectivity If you're having trouble connecting to your service: ```bash # Verify Strfry is listening locally sudo ss -tulpn | grep 7777 # Check that TOR is properly running sudo systemctl status tor # Test the local connection directly curl --include --no-buffer localhost:7777 ``` --- ## Privacy and Security Considerations Running a Nostr relay as a TOR hidden service provides several important privacy benefits: 1. **Network Privacy**: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay. 2. **Server Anonymity**: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting. 3. **Censorship Resistance**: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked. 4. **User Privacy**: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized. However, there are some important considerations: - TOR connections are typically slower than regular internet connections - Not all Nostr clients support TOR connections natively - Running a hidden service increases the importance of keeping your server secure --- Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network. For further customization and advanced configuration options, refer to the [Strfry documentation](https://github.com/hoytech/strfry). Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network! If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to [this list](https://github.com/0xtrr/onion-service-nostr-relays). Only add it if you plan to run a stable and available relay.
@ b2d670de:907f9d4a
2025-03-25 20:17:57This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users. ## Table of Contents 1. Prerequisites 2. Initial Server Setup 3. Installing Strfry Nostr Relay 4. Configuring Your Relay 5. Setting Up TOR 6. Making Your Relay Available on TOR 7. Testing Your Setup] 8. Maintenance and Security 9. Troubleshooting ## Prerequisites - A Debian or Ubuntu server - Basic familiarity with command line operations (most steps are explained in detail) - Root or sudo access to your server ## Initial Server Setup First, let's make sure your server is properly set up and secured. ### Update Your System Connect to your server via SSH and update your system: ```bash sudo apt update sudo apt upgrade -y ``` ### Set Up a Basic Firewall Install and configure a basic firewall: ```bash sudo apt install ufw -y sudo ufw allow ssh sudo ufw enable ``` This allows SSH connections while blocking other ports for security. ## Installing Strfry Nostr Relay This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the `DEPLOYMENT.md` document in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps [here](https://github.com/hoytech/strfry/blob/master/docs/DEPLOYMENT.md). ### Install Dependencies First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry: ```bash sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-dev ``` Here's why each dependency is needed: **Basic Development Tools:** - `git`: Version control system used to clone the Strfry repository and manage code updates - `build-essential`: Meta-package that includes compilers (gcc, g++), make, and other essential build tools **Perl Dependencies** (used for Strfry's build scripts): - `libyaml-perl`: Perl interface to parse YAML configuration files - `libtemplate-perl`: Template processing system used during the build process - `libregexp-grammars-perl`: Advanced regular expression handling for Perl scripts **Core Libraries for Strfry:** - `libssl-dev`: Development files for OpenSSL, used for secure connections and cryptographic operations - `zlib1g-dev`: Compression library that Strfry uses to reduce data size - `liblmdb-dev`: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend - `libflatbuffers-dev`: Memory-efficient serialization library for structured data - `libsecp256k1-dev`: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures - `libzstd-dev`: Fast real-time compression algorithm for efficient data storage and transmission ### Clone and Build Strfry Clone the Strfry repository: ```bash git clone https://github.com/hoytech/strfry.git cd strfry ``` Build Strfry: ```bash git submodule update --init make setup-golpe make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores) ``` This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime. ### Install Strfry Install the Strfry binary to your system path: ```bash sudo cp strfry /usr/local/bin ``` This makes the `strfry` command available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions. ## Configuring Your Relay ### Create Strfry User Create a dedicated user for running Strfry. This enhances security by isolating the relay process: ```bash sudo useradd -M -s /usr/sbin/nologin strfry ``` The `-M` flag prevents creating a home directory, and `-s /usr/sbin/nologin` prevents anyone from logging in as this user. This is a security best practice for service accounts. ### Create Data Directory Create a directory for Strfry's data: ```bash sudo mkdir /var/lib/strfry sudo chown strfry:strfry /var/lib/strfry sudo chmod 755 /var/lib/strfry ``` This creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it. ### Configure Strfry Copy the sample configuration file: ```bash sudo cp strfry.conf /etc/strfry.conf ``` Edit the configuration file: ```bash sudo nano /etc/strfry.conf ``` Modify the database path: ``` # Find this line: db = "./strfry-db/" # Change it to: db = "/var/lib/strfry/" ``` Check your system's hard limit for file descriptors: ```bash ulimit -Hn ``` Update the `nofiles` setting in your configuration to match this value (or set to 0): ``` # Add or modify this line in the config (example if your limit is 524288): nofiles = 524288 ``` The `nofiles` setting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular. You might also want to customize your relay's information in the config file. Look for the `info` section and update it with your relay's name, description, and other details. Set ownership of the configuration file: ```bash sudo chown strfry:strfry /etc/strfry.conf ``` ### Create Systemd Service Create a systemd service file for managing Strfry: ```bash sudo nano /etc/systemd/system/strfry.service ``` Add the following content: ```ini [Unit] Description=strfry relay service [Service] User=strfry ExecStart=/usr/local/bin/strfry relay Restart=on-failure RestartSec=5 ProtectHome=yes NoNewPrivileges=yes ProtectSystem=full LimitCORE=1000000000 [Install] WantedBy=multi-user.target ``` This systemd service configuration: - Runs Strfry as the dedicated strfry user - Automatically restarts the service if it fails - Implements security measures like `ProtectHome` and `NoNewPrivileges` - Sets resource limits appropriate for a relay Enable and start the service: ```bash sudo systemctl enable strfry.service sudo systemctl start strfry ``` Check the service status: ```bash sudo systemctl status strfry ``` ### Verify Relay is Running Test that your relay is running locally: ```bash curl localhost:7777 ``` You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR. ## Setting Up TOR Now let's make your relay accessible as a TOR hidden service. ### Install TOR Install TOR from the package repositories: ```bash sudo apt install -y tor ``` This installs the TOR daemon that will create and manage your hidden service. ### Configure TOR Edit the TOR configuration file: ```bash sudo nano /etc/tor/torrc ``` Scroll down to wherever you see a commented out part like this: ``` #HiddenServiceDir /var/lib/tor/hidden_service/ #HiddenServicePort 80 127.0.0.1:80 ``` Under those lines, add the following lines to set up a hidden service for your relay: ``` HiddenServiceDir /var/lib/tor/strfry-relay/ HiddenServicePort 80 127.0.0.1:7777 ``` This configuration: - Creates a hidden service directory at `/var/lib/tor/strfry-relay/` - Maps port 80 on your .onion address to port 7777 on your local machine - Keeps all traffic encrypted within the TOR network Create the directory for your hidden service: ```bash sudo mkdir -p /var/lib/tor/strfry-relay/ sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/ sudo chmod 700 /var/lib/tor/strfry-relay/ ``` The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys. Restart TOR to apply changes: ```bash sudo systemctl restart tor ``` ## Making Your Relay Available on TOR ### Get Your Onion Address After restarting TOR, you can find your onion address: ```bash sudo cat /var/lib/tor/strfry-relay/hostname ``` This will output something like `abcdefghijklmnopqrstuvwxyz234567.onion`, which is your relay's unique .onion address. This is what you'll share with others to access your relay. ### Understanding Onion Addresses The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key. Your users will need to use this address with the WebSocket protocol prefix to connect: `ws://youronionaddress.onion` ## Testing Your Setup ### Test with a Nostr Client The best way to test your relay is with an actual Nostr client that supports TOR: 1. Open your TOR browser 2. Go to your favorite client, either on clearnet or an onion service. - Check out [this list](https://github.com/0xtrr/onion-service-nostr-clients?tab=readme-ov-file#onion-service-nostr-clients) of nostr clients available over TOR. 3. Add your relay URL: `ws://youronionaddress.onion` to your relay list 4. Try posting a note and see if it appears on your relay - In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay. - Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected. Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too). ## Maintenance and Security ### Regular Updates Keep your system, TOR, and relay updated: ```bash # Update system sudo apt update sudo apt upgrade -y # Update Strfry cd ~/strfry git pull git submodule update make -j2 sudo cp strfry /usr/local/bin sudo systemctl restart strfry # Verify TOR is still running properly sudo systemctl status tor ``` Regular updates are crucial for security, especially for TOR which may have security-critical updates. ### Database Management Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups. ### Monitoring Logs To monitor your Strfry logs: ```bash sudo journalctl -u strfry -f ``` To check TOR logs: ```bash sudo journalctl -u tor -f ``` Monitoring logs helps you identify potential issues and understand how your relay is being used. ### Backup This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server. ```bash # Stop the relay temporarily sudo systemctl stop strfry # Backup the database sudo cp -r /var/lib/strfry /path/to/backup/location # Restart the relay sudo systemctl start strfry ``` Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it. ```bash sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/location ``` ## Troubleshooting ### Relay Not Starting If your relay doesn't start: ```bash # Check logs sudo journalctl -u strfry -e # Verify configuration cat /etc/strfry.conf # Check permissions ls -la /var/lib/strfry ``` Common issues include: - Incorrect configuration format - Permission problems with the data directory - Port already in use (another service using port 7777) - Issues with setting the nofiles limit (setting it too big) ### TOR Hidden Service Not Working If your TOR hidden service is not accessible: ```bash # Check TOR logs sudo journalctl -u tor -e # Verify TOR is running sudo systemctl status tor # Check onion address sudo cat /var/lib/tor/strfry-relay/hostname # Verify TOR configuration sudo cat /etc/tor/torrc ``` Common TOR issues include: - Incorrect directory permissions - TOR service not running - Incorrect port mapping in torrc ### Testing Connectivity If you're having trouble connecting to your service: ```bash # Verify Strfry is listening locally sudo ss -tulpn | grep 7777 # Check that TOR is properly running sudo systemctl status tor # Test the local connection directly curl --include --no-buffer localhost:7777 ``` --- ## Privacy and Security Considerations Running a Nostr relay as a TOR hidden service provides several important privacy benefits: 1. **Network Privacy**: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay. 2. **Server Anonymity**: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting. 3. **Censorship Resistance**: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked. 4. **User Privacy**: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized. However, there are some important considerations: - TOR connections are typically slower than regular internet connections - Not all Nostr clients support TOR connections natively - Running a hidden service increases the importance of keeping your server secure --- Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network. For further customization and advanced configuration options, refer to the [Strfry documentation](https://github.com/hoytech/strfry). Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network! If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to [this list](https://github.com/0xtrr/onion-service-nostr-relays). Only add it if you plan to run a stable and available relay. @ bc52210b:20bfc6de
2025-03-25 20:17:22CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient. This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off! Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now. --- **CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused!** Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why: * Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs). * Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key. **Key Differences:** 1. What’s Aggregated? * CISA: Aggregates signatures. * Key Aggregation: Aggregates public keys. 2. What the Verifier Needs * CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature. * Key Aggregation: The verifier only needs the single aggregated public key and one message. 3. When It Happens * CISA: Used during transaction signing, when inputs are being combined into a transaction. * MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control. So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs! --- **Two Flavors of CISA: Half-Agg and Full-Agg** CISA comes in two modes: * Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.) * Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later. Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg. --- **Half Signature Aggregation (Half-Agg) Explained** **How It Works** Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process: 1. Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers. 2. Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature. A Schnorr signature has two parts: * R: A random point (32 bytes). * s: A scalar value (32 bytes). In Half-Agg: * The R values from each signature are kept separate (one per input). * The s values from all signatures are combined into a single s value. **Why It Saves Space (~50%)** Let’s break down the size savings with some math: Before Aggregation: * Each Schnorr signature = 64 bytes (32 for R + 32 for s). * For n inputs: n × 64 bytes. After Half-Agg: * Keep n R values (32 bytes each) = 32 × n bytes. * Combine all s values into one = 32 bytes. * Total size: 32 × n + 32 bytes. Comparison: * Original: 64n bytes. * Half-Agg: 32n + 32 bytes. * For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings! **Real-World Impact:** Based on recent Bitcoin usage, Half-Agg could save: * ~19.3% in space (reducing transaction size). * ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA. --- **Applications of Half-Agg** Half-Agg isn’t just a cool idea—it has practical uses: 1. Transaction-wide Aggregation * Combine all signatures within a single transaction. * Result: Smaller transactions, lower fees. 2. Block-wide Aggregation * Combine signatures across all transactions in a Bitcoin block. * Result: Even bigger space savings at the blockchain level. 3. Off-chain Protocols / P2P * Use Half-Agg in systems like Lightning Network gossip messages. * Benefit: Efficiency without needing miners or a Bitcoin soft fork. --- **Challenges with Half-Agg** While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level: 1. Breaking Adaptor Signatures * Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges. * Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on. 2. Impact on Reorg Recovery * In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed. * If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery. These challenges mean Half-Agg needs careful design, especially for block-wide use. --- **Wrapping Up** CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning. But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future!
@ bc52210b:20bfc6de
2025-03-25 20:17:22CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient. This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off! Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now. --- **CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused!** Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why: * Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs). * Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key. **Key Differences:** 1. What’s Aggregated? * CISA: Aggregates signatures. * Key Aggregation: Aggregates public keys. 2. What the Verifier Needs * CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature. * Key Aggregation: The verifier only needs the single aggregated public key and one message. 3. When It Happens * CISA: Used during transaction signing, when inputs are being combined into a transaction. * MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control. So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs! --- **Two Flavors of CISA: Half-Agg and Full-Agg** CISA comes in two modes: * Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.) * Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later. Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg. --- **Half Signature Aggregation (Half-Agg) Explained** **How It Works** Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process: 1. Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers. 2. Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature. A Schnorr signature has two parts: * R: A random point (32 bytes). * s: A scalar value (32 bytes). In Half-Agg: * The R values from each signature are kept separate (one per input). * The s values from all signatures are combined into a single s value. **Why It Saves Space (~50%)** Let’s break down the size savings with some math: Before Aggregation: * Each Schnorr signature = 64 bytes (32 for R + 32 for s). * For n inputs: n × 64 bytes. After Half-Agg: * Keep n R values (32 bytes each) = 32 × n bytes. * Combine all s values into one = 32 bytes. * Total size: 32 × n + 32 bytes. Comparison: * Original: 64n bytes. * Half-Agg: 32n + 32 bytes. * For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings! **Real-World Impact:** Based on recent Bitcoin usage, Half-Agg could save: * ~19.3% in space (reducing transaction size). * ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA. --- **Applications of Half-Agg** Half-Agg isn’t just a cool idea—it has practical uses: 1. Transaction-wide Aggregation * Combine all signatures within a single transaction. * Result: Smaller transactions, lower fees. 2. Block-wide Aggregation * Combine signatures across all transactions in a Bitcoin block. * Result: Even bigger space savings at the blockchain level. 3. Off-chain Protocols / P2P * Use Half-Agg in systems like Lightning Network gossip messages. * Benefit: Efficiency without needing miners or a Bitcoin soft fork. --- **Challenges with Half-Agg** While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level: 1. Breaking Adaptor Signatures * Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges. * Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on. 2. Impact on Reorg Recovery * In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed. * If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery. These challenges mean Half-Agg needs careful design, especially for block-wide use. --- **Wrapping Up** CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning. But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future! @ b17fccdf:b7211155
2025-03-25 11:23:36Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la [guía de MiniBolt](https://minbolt.info/). Esto tiene una **razón**, por supuesto una **solución**, además de una **conclusión**. Sin entrar en demasiados detalles: ## La razón El **bloqueo a Cloudflare**, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una [orden judicial](https://www.poderjudicial.es/search/AN/openDocument/3c85bed480cbb1daa0a8778d75e36f0d/20221004) emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización. Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo [ECH](https://developers.cloudflare.com/ssl/edge-certificates/ech) (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar **bloqueos basados en dominios**, lo que les obliga a recurrir a **bloqueos más amplios por IP o rangos de IP** para cumplir con la orden judicial. Esta práctica tiene **consecuencias graves**, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un **perjuicio para terceros**, **restringiendo el acceso a muchos dominios legítimos** que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la [web de MiniBolt](https://minibolt.minibolt.info) y su dominio `minibolt.info`, los cuales **utilizan Cloudflare como proxy** para aprovechar las medidas de **seguridad, privacidad, optimización y servicios** adicionales que la plataforma ofrece de forma gratuita. Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.  ## La solución Obviamente, **MiniBolt no dejará de usar Cloudflare** como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para **evitar esta restricción** y poder acceder: **~>** Utiliza **una VPN**: Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad: - [IVPN](https://www.ivpn.net/es/) - [Mullvad VPN](https://mullvad.net/es/vpn) - [Proton VPN](https://protonvpn.com/es-es) (**gratis**) - [Obscura VPN](https://obscura.net/) (**solo para macOS**) - [Cloudfare WARP](https://developers.cloudflare.com/cloudflare-one/connections/connect-devices/warp/download-warp/) (**gratis**) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos: 1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy" 2. Marca la casilla "Habilite el modo proxy en este dispositivo" 3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias 4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio. 3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a [esta](https://minibolt.minibolt.info/system/system/privacy#example-from-firefox) para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la [guía de MiniBolt](https://minibolt.minibolt.info/) sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info [AQUÍ](https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958).  **~>** [**Proxifica tu navegador para usar la red de Tor**](https://minibolt.minibolt.info/system/system/privacy#ssh-remote-access-through-tor), o utiliza el [**navegador oficial de Tor**](https://www.torproject.org/es/download/) (recomendado).  ## La conclusión Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la [Declaración de Independencia del Ciberespacio](https://es.wikisource.org/wiki/Declaraci%C3%B3n_de_independencia_del_ciberespacio) que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad. Es momento de actuar y estar preparados: debemos **impulsar el desarrollo y la difusión** de las **herramientas anticensura** que tenemos a nuestro alcance, protegiendo así la **libertad digital** y asegurando un acceso equitativo a la información para todos Este compromiso es uno de los **pilares fundamentales de MiniBolt,** lo que convierte este desafío en una oportunidad para poner a prueba las **soluciones anticensura** [ya disponibles](https://minibolt.minibolt.info/bonus-guides/system/tor-services), así como **las que están en camino**. ¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!  --- Fuentes: * https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239 * https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257 * https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958 * https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689 * https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007
@ b17fccdf:b7211155
2025-03-25 11:23:36Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la [guía de MiniBolt](https://minbolt.info/). Esto tiene una **razón**, por supuesto una **solución**, además de una **conclusión**. Sin entrar en demasiados detalles: ## La razón El **bloqueo a Cloudflare**, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una [orden judicial](https://www.poderjudicial.es/search/AN/openDocument/3c85bed480cbb1daa0a8778d75e36f0d/20221004) emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización. Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo [ECH](https://developers.cloudflare.com/ssl/edge-certificates/ech) (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar **bloqueos basados en dominios**, lo que les obliga a recurrir a **bloqueos más amplios por IP o rangos de IP** para cumplir con la orden judicial. Esta práctica tiene **consecuencias graves**, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un **perjuicio para terceros**, **restringiendo el acceso a muchos dominios legítimos** que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la [web de MiniBolt](https://minibolt.minibolt.info) y su dominio `minibolt.info`, los cuales **utilizan Cloudflare como proxy** para aprovechar las medidas de **seguridad, privacidad, optimización y servicios** adicionales que la plataforma ofrece de forma gratuita. Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.  ## La solución Obviamente, **MiniBolt no dejará de usar Cloudflare** como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para **evitar esta restricción** y poder acceder: **~>** Utiliza **una VPN**: Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad: - [IVPN](https://www.ivpn.net/es/) - [Mullvad VPN](https://mullvad.net/es/vpn) - [Proton VPN](https://protonvpn.com/es-es) (**gratis**) - [Obscura VPN](https://obscura.net/) (**solo para macOS**) - [Cloudfare WARP](https://developers.cloudflare.com/cloudflare-one/connections/connect-devices/warp/download-warp/) (**gratis**) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos: 1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy" 2. Marca la casilla "Habilite el modo proxy en este dispositivo" 3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias 4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio. 3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a [esta](https://minibolt.minibolt.info/system/system/privacy#example-from-firefox) para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la [guía de MiniBolt](https://minibolt.minibolt.info/) sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info [AQUÍ](https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958).  **~>** [**Proxifica tu navegador para usar la red de Tor**](https://minibolt.minibolt.info/system/system/privacy#ssh-remote-access-through-tor), o utiliza el [**navegador oficial de Tor**](https://www.torproject.org/es/download/) (recomendado).  ## La conclusión Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la [Declaración de Independencia del Ciberespacio](https://es.wikisource.org/wiki/Declaraci%C3%B3n_de_independencia_del_ciberespacio) que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad. Es momento de actuar y estar preparados: debemos **impulsar el desarrollo y la difusión** de las **herramientas anticensura** que tenemos a nuestro alcance, protegiendo así la **libertad digital** y asegurando un acceso equitativo a la información para todos Este compromiso es uno de los **pilares fundamentales de MiniBolt,** lo que convierte este desafío en una oportunidad para poner a prueba las **soluciones anticensura** [ya disponibles](https://minibolt.minibolt.info/bonus-guides/system/tor-services), así como **las que están en camino**. ¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!  --- Fuentes: * https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239 * https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257 * https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958 * https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689 * https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007 @ 3b7fc823:e194354f
2025-03-23 03:54:16A quick guide for the less than technical savvy to set up their very own free private tor enabled email using Onionmail. Privacy is for everyone, not just the super cyber nerds. Onion Mail is an anonymous POP3/SMTP email server program hosted by various people on the internet. You can visit this site and read the details: https://en.onionmail.info/ 1. Download Tor Browser First, if you don't already, go download Tor Browser. You are going to need it. https://www.torproject.org/ 2. Sign Up Using Tor browser go to the directory page (https://onionmail.info/directory.html) choose one of the servers and sign up for an account. I say sign up but it is just choosing a user name you want to go before the @xyz.onion email address and solving a captcha. 3. Account information Once you are done signing up an Account information page will pop up. **MAKE SURE YOU SAVE THIS!!!** It has your address and passwords (for sending and receiving email) that you will need. If you lose them then you are shit out of luck. 4. Install an Email Client You can use Claws Mail, Neomutt, or whatever, but for this example, we will be using Thunderbird. a. Download Thunderbird email client b. The easy setup popup page that wants your name, email, and password isn't going to like your user@xyz.onion address. Just enter something that looks like a regular email address such as name@example.com and the **Configure Manually**option will appear below. Click that. 5. Configure Incoming (POP3) Server Under Incoming Server: Protocol: POP3 Server or Hostname: xyz.onion (whatever your account info says) Port: 110 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (POP3 password). 6. Configure Outgoing (SMTP) Server Under Outgoing Server: Server or Hostname: xyz.onion (whatever your account info says) Port: 25 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (SMTP password). 7. Click on email at the top and change your address if you had to use a spoof one to get the configure manually to pop up. 8. Configure Proxy a. Click the **gear icon** on the bottom left for settings. Scroll all the way down to **Network & Disk Space**. Click the **settings button** next to **Connection. Configure how Thunderbird connects to the internet**. b. Select **Manual Proxy Configuration**. For **SOCKS Host** enter **127.0.0.1** and enter port **9050**. (if you are running this through a VM the port may be different) c. Now check the box for **SOCKS5** and then **Proxy DNS when using SOCKS5** down at the bottom. Click OK 9. Check Email For thunderbird to reach the onion mail server it has to be connected to tor. Depending on your local setup, it might be fine as is or you might have to have tor browser open in the background. Click on **inbox** and then the **little cloud icon** with the down arrow to check mail. 10. Security Exception Thunderbird is not going to like that the onion mail server security certificate is self signed. A popup **Add Security Exception** will appear. Click **Confirm Security Exception**. You are done. Enjoy your new private email service. **REMEMBER: The server can read your emails unless they are encrypted. Go into account settings. Look down and click End-toEnd Encryption. Then add your OpenPGP key or open your OpenPGP Key Manager (you might have to download one if you don't already have one) and generate a new key for this account.**
@ 3b7fc823:e194354f
2025-03-23 03:54:16A quick guide for the less than technical savvy to set up their very own free private tor enabled email using Onionmail. Privacy is for everyone, not just the super cyber nerds. Onion Mail is an anonymous POP3/SMTP email server program hosted by various people on the internet. You can visit this site and read the details: https://en.onionmail.info/ 1. Download Tor Browser First, if you don't already, go download Tor Browser. You are going to need it. https://www.torproject.org/ 2. Sign Up Using Tor browser go to the directory page (https://onionmail.info/directory.html) choose one of the servers and sign up for an account. I say sign up but it is just choosing a user name you want to go before the @xyz.onion email address and solving a captcha. 3. Account information Once you are done signing up an Account information page will pop up. **MAKE SURE YOU SAVE THIS!!!** It has your address and passwords (for sending and receiving email) that you will need. If you lose them then you are shit out of luck. 4. Install an Email Client You can use Claws Mail, Neomutt, or whatever, but for this example, we will be using Thunderbird. a. Download Thunderbird email client b. The easy setup popup page that wants your name, email, and password isn't going to like your user@xyz.onion address. Just enter something that looks like a regular email address such as name@example.com and the **Configure Manually**option will appear below. Click that. 5. Configure Incoming (POP3) Server Under Incoming Server: Protocol: POP3 Server or Hostname: xyz.onion (whatever your account info says) Port: 110 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (POP3 password). 6. Configure Outgoing (SMTP) Server Under Outgoing Server: Server or Hostname: xyz.onion (whatever your account info says) Port: 25 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (SMTP password). 7. Click on email at the top and change your address if you had to use a spoof one to get the configure manually to pop up. 8. Configure Proxy a. Click the **gear icon** on the bottom left for settings. Scroll all the way down to **Network & Disk Space**. Click the **settings button** next to **Connection. Configure how Thunderbird connects to the internet**. b. Select **Manual Proxy Configuration**. For **SOCKS Host** enter **127.0.0.1** and enter port **9050**. (if you are running this through a VM the port may be different) c. Now check the box for **SOCKS5** and then **Proxy DNS when using SOCKS5** down at the bottom. Click OK 9. Check Email For thunderbird to reach the onion mail server it has to be connected to tor. Depending on your local setup, it might be fine as is or you might have to have tor browser open in the background. Click on **inbox** and then the **little cloud icon** with the down arrow to check mail. 10. Security Exception Thunderbird is not going to like that the onion mail server security certificate is self signed. A popup **Add Security Exception** will appear. Click **Confirm Security Exception**. You are done. Enjoy your new private email service. **REMEMBER: The server can read your emails unless they are encrypted. Go into account settings. Look down and click End-toEnd Encryption. Then add your OpenPGP key or open your OpenPGP Key Manager (you might have to download one if you don't already have one) and generate a new key for this account.** @ 21335073:a244b1ad
2025-03-18 20:47:50**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
@ 21335073:a244b1ad
2025-03-18 20:47:50**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation. @ 21335073:a244b1ad
2025-03-18 14:43:08**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
@ 21335073:a244b1ad
2025-03-18 14:43:08**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation. @ a07fae46:7d83df92
2025-03-18 12:31:40if the JFK documents come out and are nothing but old hat, it will be disappointing. but if they contain revelations, then they are an unalloyed good. unprecedented and extraordinary; worthy of praise and admiration. they murdered the president in broad daylight and kept 80,000 related documents secret for 60 years. the apparatus that did that and got away with it, is 100+ years in the making. the magic bullet was just the starting pistol of a new *era*; a *level up* in an [old game](https://archive.org/details/TragedyAndHope_501/page/n5/mode/2up?q=feudalist+fashion). it won't be dismantled and your republic delivered back with a bow in *2 months*. have a little humility and a little gratitude. cynicism is easy. it's peak mid-wittery. yeah no shit everything is corrupt and everyone's likely captured by [AIPAC](https://books.google.com/books/publisher/content?id=gKVKDwAAQBAJ&pg=PT68&img=1&zoom=3&hl=en&bul=1&sig=ACfU3U2pagVXTYdJOKxkAwmmFQpuSnoS5g&w=1280) or something beyond. YOU THINK AIPAC is the [ALL SEEING EYE](https://archive.org/details/the-all-seeing-eye-vol-1-5-manly-p.-hall-may-1923-sept-1931)? you can keep going, if you want to, but have some awareness and appreciation for where we are and what it took to get here. the first 'you are fake news' was also a shot heard 'round the world and you are riding high on it's [Infrasound](https://en.wikipedia.org/wiki/Infrasound) wave, still reverberating; unappreciative of the profound delta in public awareness and understanding, and rate of change, that has occurred since that moment, in [2017](https://www.youtube.com/watch?v=Vqpzk-qGxMU). think about where we were back then, especially with corporate capture of the narrative. trump's bullheaded behavior, if only ego-driven, *is* what broke the spell. an *actual* moment of savage bravery is what allows for your current jaded affectation. black pilled is boring. it's intellectually lazy. it is low-resolution-thinking, no better than progressives who explain the myriad ills of the world through 'racism'. normalcy bias works both ways. i'm not grading you on a curve that includes NPCs. i'm grading you against those of us with a mind, on up. do better. the best Webb-style doomer argument is essentially 'the mouse trap needs a piece of cheese in order to work'. ok, but it doesn't need 3 pieces of cheese, or 5. was FreeRoss the piece of cheese? was the SBR the cheese? real bitcoiners know how dumb the 'sbr is an attempt to takeover btc' narrative is, so extrapolate from that. what about withdrawal from the WHO? freeze and review of USAID et al? how many pieces of cheese before we realize it's not a trap? it's just a messy endeavor. Good morning. #jfkFiles #nostrOnly
@ a07fae46:7d83df92
2025-03-18 12:31:40if the JFK documents come out and are nothing but old hat, it will be disappointing. but if they contain revelations, then they are an unalloyed good. unprecedented and extraordinary; worthy of praise and admiration. they murdered the president in broad daylight and kept 80,000 related documents secret for 60 years. the apparatus that did that and got away with it, is 100+ years in the making. the magic bullet was just the starting pistol of a new *era*; a *level up* in an [old game](https://archive.org/details/TragedyAndHope_501/page/n5/mode/2up?q=feudalist+fashion). it won't be dismantled and your republic delivered back with a bow in *2 months*. have a little humility and a little gratitude. cynicism is easy. it's peak mid-wittery. yeah no shit everything is corrupt and everyone's likely captured by [AIPAC](https://books.google.com/books/publisher/content?id=gKVKDwAAQBAJ&pg=PT68&img=1&zoom=3&hl=en&bul=1&sig=ACfU3U2pagVXTYdJOKxkAwmmFQpuSnoS5g&w=1280) or something beyond. YOU THINK AIPAC is the [ALL SEEING EYE](https://archive.org/details/the-all-seeing-eye-vol-1-5-manly-p.-hall-may-1923-sept-1931)? you can keep going, if you want to, but have some awareness and appreciation for where we are and what it took to get here. the first 'you are fake news' was also a shot heard 'round the world and you are riding high on it's [Infrasound](https://en.wikipedia.org/wiki/Infrasound) wave, still reverberating; unappreciative of the profound delta in public awareness and understanding, and rate of change, that has occurred since that moment, in [2017](https://www.youtube.com/watch?v=Vqpzk-qGxMU). think about where we were back then, especially with corporate capture of the narrative. trump's bullheaded behavior, if only ego-driven, *is* what broke the spell. an *actual* moment of savage bravery is what allows for your current jaded affectation. black pilled is boring. it's intellectually lazy. it is low-resolution-thinking, no better than progressives who explain the myriad ills of the world through 'racism'. normalcy bias works both ways. i'm not grading you on a curve that includes NPCs. i'm grading you against those of us with a mind, on up. do better. the best Webb-style doomer argument is essentially 'the mouse trap needs a piece of cheese in order to work'. ok, but it doesn't need 3 pieces of cheese, or 5. was FreeRoss the piece of cheese? was the SBR the cheese? real bitcoiners know how dumb the 'sbr is an attempt to takeover btc' narrative is, so extrapolate from that. what about withdrawal from the WHO? freeze and review of USAID et al? how many pieces of cheese before we realize it's not a trap? it's just a messy endeavor. Good morning. #jfkFiles #nostrOnly @ bc52210b:20bfc6de
2025-03-14 20:39:20When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract. The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable. In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions. Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure.
@ bc52210b:20bfc6de
2025-03-14 20:39:20When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract. The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable. In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions. Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure. @ df173277:4ec96708
2025-02-07 00:41:34## **Building Our Confidential Backend on Secure Enclaves** With our newly released [private and confidential **Maple AI**](https://trymaple.ai/?ref=blog.opensecret.cloud) and the open sourcing of our [**OpenSecret** platform](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud) code, I'm excited to present this technical primer on how we built our confidential compute platform leveraging **secure enclaves**. By combining AWS Nitro enclaves with end-to-end encryption and reproducible builds, our platform gives developers and end users the confidence that user data is protected, even at runtime, and that the code operating on their data has not been tampered with. ## **Auth and Databases Today** As developers, we live in an era where protecting user data means "encryption at rest," plus some access policies and procedures. Developers typically run servers that: 1. Need to register users (authentication). 2. Collect and process user data in business-specific ways, often on the backend. Even if data is encrypted at rest, it's commonly unlocked with a single master key or credentials the server holds. This means that data is visible during runtime to the application, system administrators, and potentially to the hosting providers. This scenario makes it difficult (or impossible) to guarantee that sensitive data isn't snooped on, memory-dumped, or used in unauthorized ways (for instance, training AI models behind the scenes). ## **"Just Trust Us" Isn't Good Enough** In a traditional server architecture, users have to take it on faith that the code handling their data is the same code the operator claims to be running. Behind the scenes, applications can be modified or augmented to forward private information elsewhere, and there is no transparent way for users to verify otherwise. This lack of proof is unsettling, especially for services that process or store highly confidential data. Administrators, developers, or cloud providers with privileged access can inspect memory in plaintext, attach debuggers, or gain complete visibility into stored information. Hackers who compromise these privileged levels can directly access sensitive data. Even with strict policies or promises of good conduct, the reality is that technical capabilities and misconfigurations can override words on paper. If a server master key can decrypt your data or can be accessed by an insider with root permissions, then "just trust us" loses much of its credibility. The rise of AI platforms amplifies this dilemma. User data, often full of personal details, gets funneled into large-scale models that might be training or fine-tuning behind the scenes. Relying on vague assurances that "we don't look at your data" is no longer enough to prevent legitimate concerns about privacy and misuse. Now more than ever, providing a **strong, verifiable** guarantee that data remains off-limits, even when actively processed, has become a non-negotiable requirement for trustworthy services. ## **Current Attempts at Securing Data** 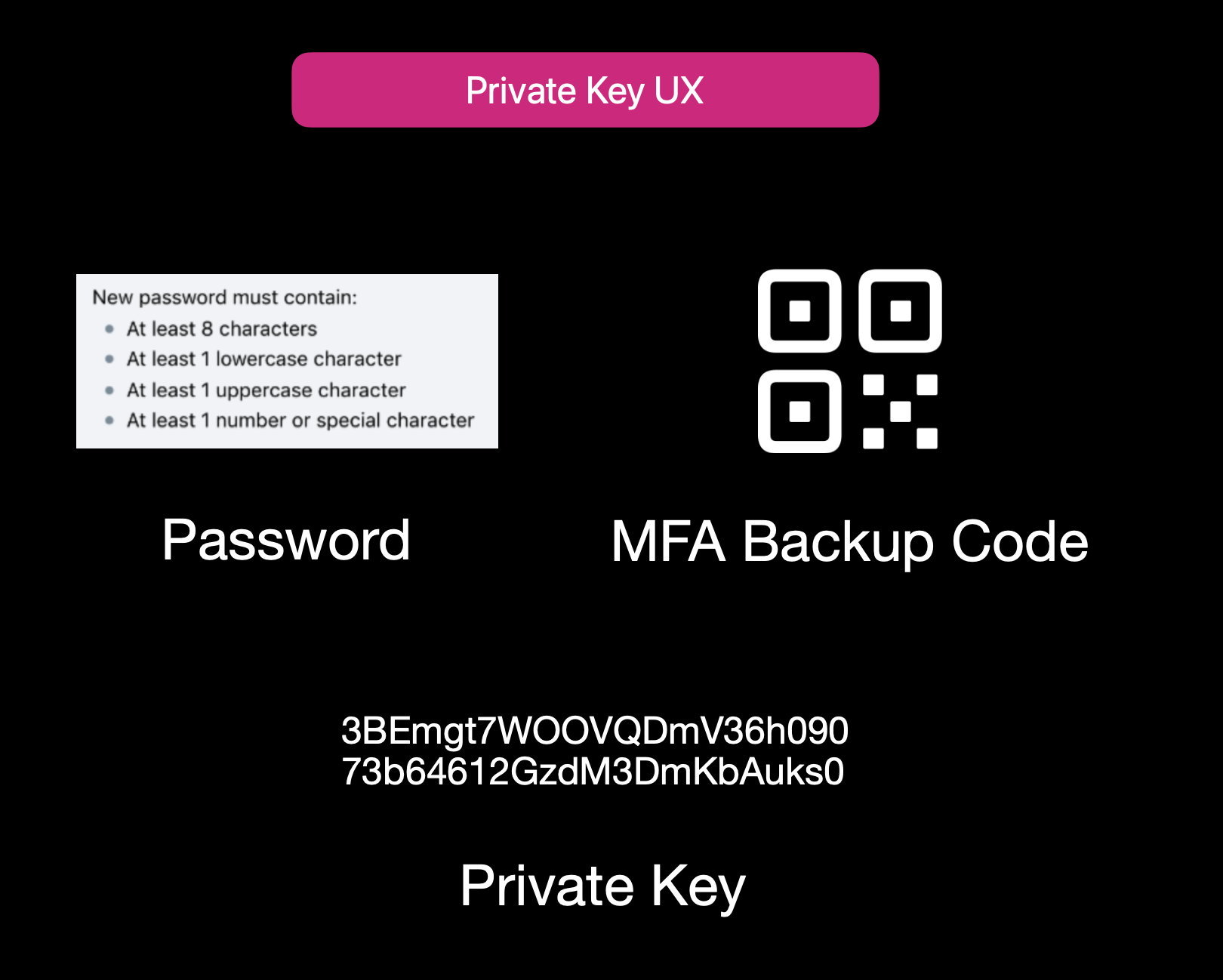Current User Experience of E2EE Apps While properly securing data is not easy, it isn't to say that no one is trying. Some solutions use **end-to-end encryption** (E2EE), where user data is encrypted client-side with a password or passphrase, so not even the server operator can decrypt it. That approach can be quite secure, but it also has its **limitations**: 1. **Key Management Nightmares**: If a user forgets their passphrase, the data is effectively lost, and there's no way to recover it from the developer's side. 2. **Feature Limitations**: Complex server-side operations (like offline/background tasks, AI queries, real-time collaboration, or heavy computation) can't easily happen if the server is never capable of processing decrypted data. 3. **Platform Silos**: Some solutions rely on iCloud, Google Drive, or local device storage. That can hamper multi-device usage or multi-OS compatibility. Other approaches include self-hosting. However, these either burden users with dev ops overhead or revert to the "trust me" model for the server if you "self-host" on a cloud provider. ## **Secure Enclaves** ### **The Hybrid Approach** Secure enclaves offer a compelling middle ground. They combine the privacy benefits of keeping data secure from prying admins while still allowing meaningful server-side computation. In a nutshell, an enclave is a protected environment within a machine, isolated at the hardware level, so that even if the OS or server is compromised, the data and code inside the enclave remain hidden. 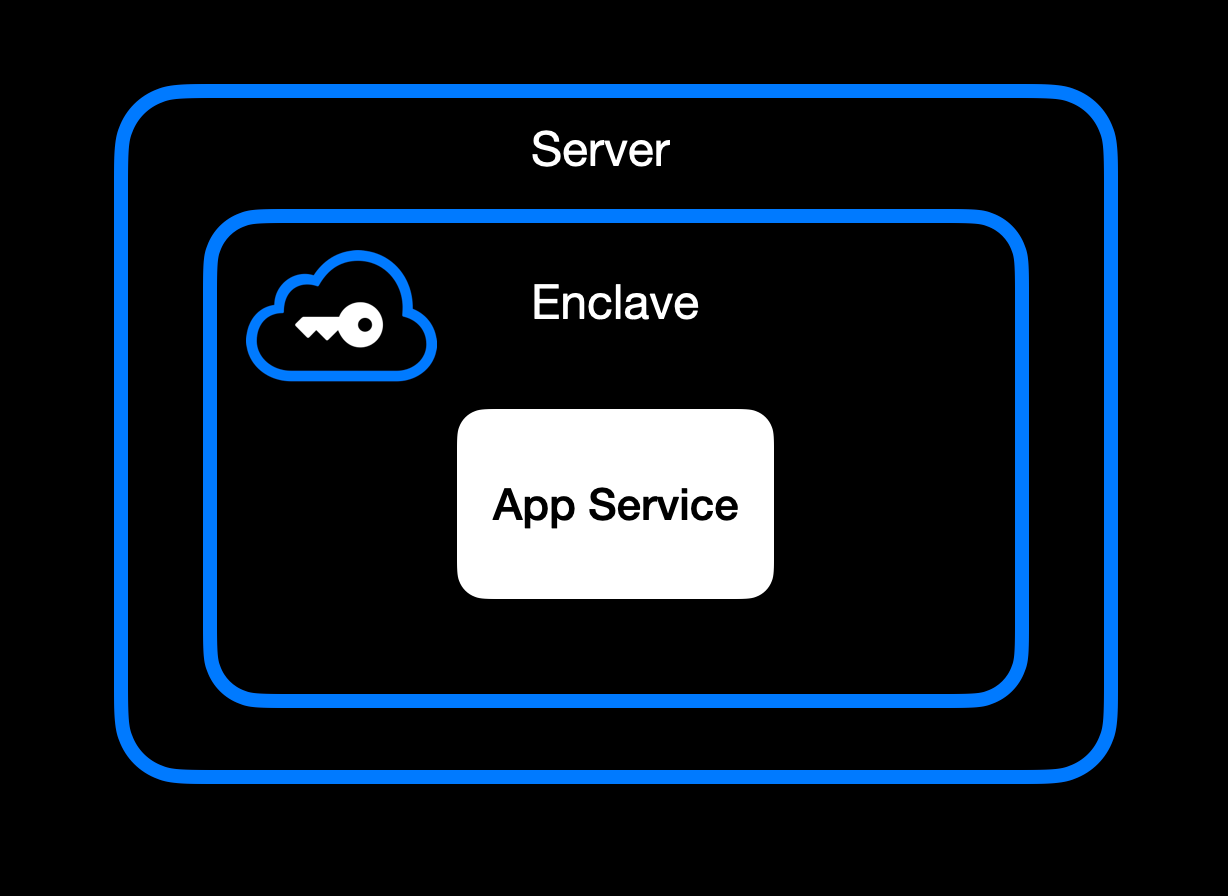App Service Running Inside Secure Enclave ### **High-Level Goal of Enclaves** Enclaves, also known under the broader umbrella of **confidential computing**, aim to:\ • **Lock down data** so that only authorized code within the enclave can process the original plaintext data.\ • **Deny external inspection** by memory dumping, attaching a debugger, or intercepting plaintext network traffic.\ • **Prove** to external users or services that an enclave is running unmodified, approved code (this is where **remote attestation** comes in). ### **Different Secure Enclave Solutions** [**AMD SEV**](https://www.amd.com/en/developer/sev.html?ref=blog.opensecret.cloud) **(Secure Encrypted Virtualization)** encrypts an entire virtual machine's memory so that even a compromised hypervisor cannot inspect or modify guest data. Its core concept is "lift-and-shift" security. No application refactoring is required because hardware-based encryption automatically protects the OS and all VM applications. Later enhancements (SEV-ES and SEV-SNP) added encryption of CPU register states and memory integrity protections, further limiting hypervisor tampering. This broad coverage means the guest OS is included in the trusted boundary. AMD SEV has matured into a robust solution for confidential VMs in multi-tenant clouds. [**Intel TDX**](https://www.intel.com/content/www/us/en/developer/tools/trust-domain-extensions/overview.html?ref=blog.opensecret.cloud) **(Trust Domain Extensions)** shifts from process-level enclaves to full VM encryption, allowing an entire guest operating system and its applications to run in an isolated "trust domain." Like AMD SEV, Intel TDX encrypts and protects all memory the VM uses from hypervisors or other privileged software, so developers do not need to refactor their code to benefit from hardware-based confidentiality. This broader scope addresses many SGX limitations, such as strict memory bounds and the need to split out enclave-specific logic, and offers a more straightforward "lift-and-shift" path for running existing workloads privately. While SGX is now deprecated, TDX carries forward the core confidential computing principles but applies them at the virtual machine level for more substantial isolation, easier deployment, and the ability to scale up to large, memory-intensive applications. [**Apple Secure Enclave and Private Compute**](https://security.apple.com/blog/private-cloud-compute/?ref=blog.opensecret.cloud) is a dedicated security coprocessor embedded in most Apple devices (iPhones, iPads, Macs) and now extended to Apple's server-side AI infrastructure. It runs its own microkernel, has hardware-protected memory, and securely manages operations such as biometric authentication, key storage, and cryptographic tasks. Apple's "Private Compute" approach in the cloud brings similar enclave capabilities to server-based AI, enabling on-device-grade privacy even when requests are processed in Apple's data centers. [**AWS Nitro Enclaves**](https://docs.aws.amazon.com/enclaves/latest/user/nitro-enclave.html?ref=blog.opensecret.cloud) carve out a tightly isolated "mini-VM" from a parent EC2 instance, with its own vCPUs and memory guarded by dedicated Nitro cards. The enclave has no persistent storage and no external network access, significantly reducing the attack surface. Communication with the parent instance occurs over a secure local channel (vsock), and AWS offers hardware-based attestation so that secrets (e.g., encryption keys from AWS KMS) can be accessed only to the correct enclave. This design helps developers protect sensitive data or code even if the main EC2 instance's OS is compromised. [**NVIDIA GPU TEEs**](https://www.nvidia.com/en-us/data-center/solutions/confidential-computing/?ref=blog.opensecret.cloud) **(Hopper H100 and Blackwell)** extend confidential computing to accelerated workloads by encrypting data in GPU memory and ensuring that even a privileged host cannot view or tamper with it. Data moving between CPU and GPU is encrypted in transit, so sensitive model weights or inputs remain protected during AI training or inference. NVIDIA's hardware and drivers handle secure data paths under the hood, allowing confidential large language model (LLM) workloads and other GPU-accelerated computations to run with minimal performance overhead and strong security guarantees. ### **Key Benefits** One major advantage of enclaves is their ability to **keep memory completely off-limits** to outside prying eyes. Even administrators who can normally inspect processes at will are blocked from peeking into the enclave's protected memory space. The enclave model is a huge shift in the security model: it prevents casual inspection and defends against sophisticated memory dumping techniques that might otherwise leak secrets or sensitive data. Another key benefit centers on cryptographic keys that are **never exposed outside the enclave**. Only verified code running inside the enclave environment can run decryption or signing operations, and it can only do so while that specific code is running. This ensures that compromised hosts or rogue processes, even those with high-level privileges, are unable to intercept or misuse the keys because the keys remain strictly within the trusted boundary of the hardware. Enclaves can also offer the power of **remote attestation**, allowing external clients or systems to confirm that they're speaking to an authentic, untampered enclave. By validating the hardware's integrity measurements and enclave-specific proofs, the remote party can be confident in the underlying security properties, an important guarantee in multi-tenant environments or whenever trust boundaries extend across different organizations and networks. Beyond that, **reproducible builds** can create a verifiable fingerprint proving which binary runs in the enclave. This is a step above a simple "trust us" approach. Anyone can independently recreate the enclave image and verify the resulting cryptographic hash by using a reproducible build system (for example, [our NixOS-based solution](https://github.com/OpenSecretCloud/opensecret/blob/master/flake.nix?ref=blog.opensecret.cloud)). If it matches, then users and developers know precisely how code handles their data, boosting confidence that no hidden changes exist. It's worth noting that although enclaves shield you from software devs, cloud providers, and insider threats, you do have to trust the **hardware vendor** (Intel, AMD, Apple, AWS, or NVIDIA) to implement their microcode and firmware securely. The entire enclave model could be theoretically undermined if a CPU maker's root keys or manufacturing process were compromised. Fortunately, these companies undergo extensive audits and firmware validations (often with third-party researchers), and their remote attestation mechanisms allow you to confirm specific firmware versions before trusting an enclave. While this adds a layer of "vendor trust," it's still a far more contained risk than trusting an entire operating system or cloud stack, so enclaves remain a strong step forward in practical, confidential computing. ## **How We Use Secure Enclaves** Now that we've covered the general idea of enclaves let's look at how we specifically implement them in OpenSecret, our developer platform for handling user auth, private keys, data encryption, and AI workloads. ### **Our Stack: AWS Nitro + Nvidia TEE** • **AWS Nitro Enclaves for the backend**: All critical logic, authentication, private key management, and data encryption/decryption run inside an AWS Nitro Enclave. • **Nvidia Trusted Execution for AI**: For large AI inference (such as the Llama 3.3 70B model), we utilize Nvidia's GPU-based TEEs to protect even GPU memory. This means users can feed sensitive data to the AI model **without** exposing it in plaintext to the GPU providers or us as the operator. [Edgeless Systems](https://www.edgeless.systems/?ref=blog.opensecret.cloud) is our Nvidia TEE provider, and due to the power of enclave verification, we don't need to worry about who runs the GPUs. We know requests can't be inspected or tampered with. ### **End-to-End Encryption from Client to Enclave** 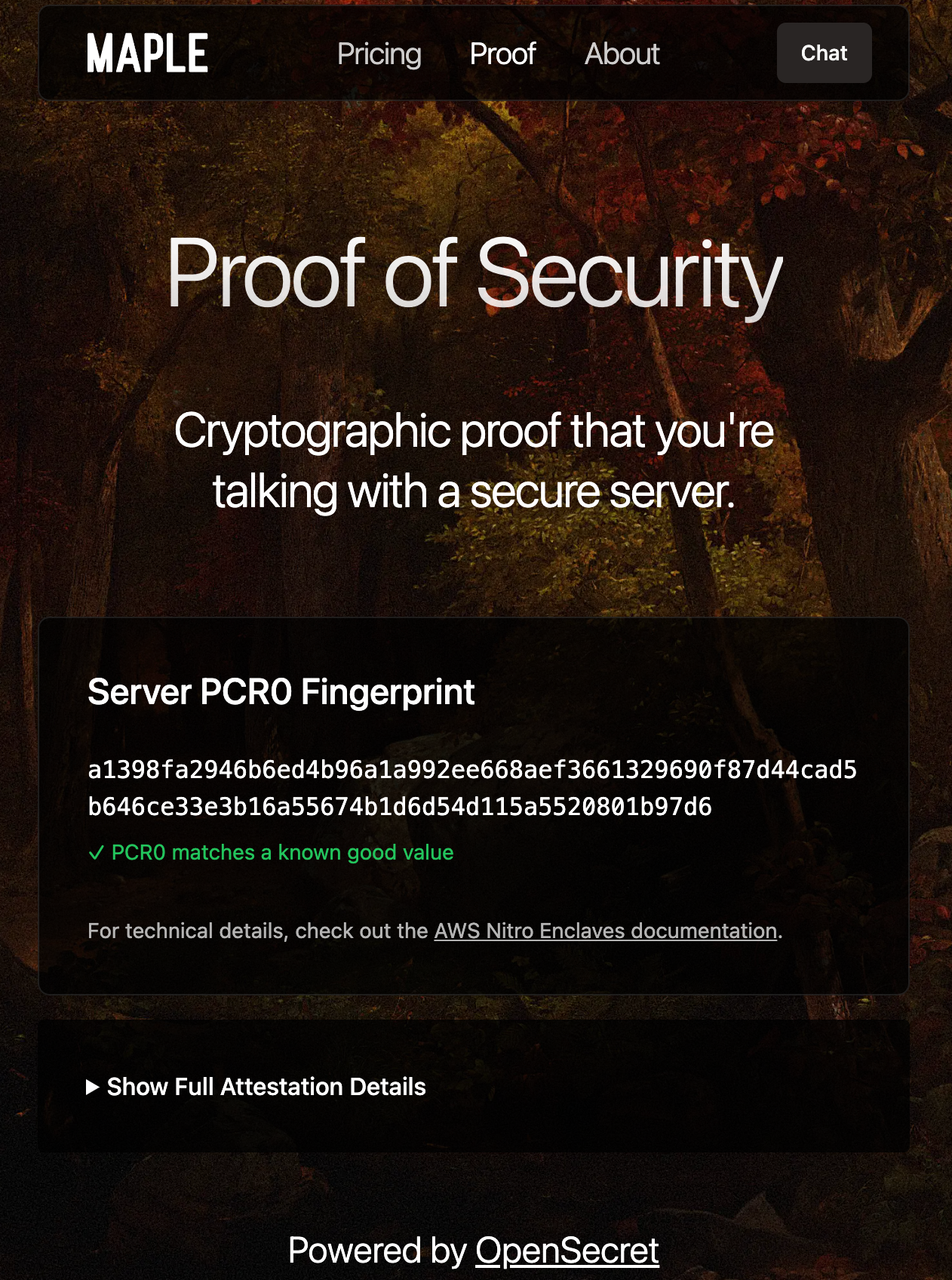Client-side Enclave Attestation from Maple AI Before login or data upload, the user/client verifies the **enclave attestation** from our platform. This process proves that the specific Nitro Enclave is genuine and runs the exact code we've published. You can check this out live on [Maple AI's attestation page](https://trymaple.ai/proof?ref=blog.opensecret.cloud). Based on the attestation, the client establishes a secure ephemeral communication channel that only that enclave can decrypt. While we take advantage of SSL, it is typically not terminated inside the enclave itself. To ensure there's full encrypted data transfer all the way through to the enclave, we establish this additional handshake based on the attestation document that is used for all API requests during the client session. From there, the user's credentials, private keys, and data pass through this secure channel directly into the enclave, where they are decrypted and processed according to the user's request. ### **In-Enclave Operations** At the core of OpenSecret's approach is the conviction that security-critical tasks must happen inside the enclave, where even administrative privileges or hypervisor-level compromise cannot expose plaintext data. This encompasses everything from when a user logs in to creating and managing sensitive cryptographic keys. By confining these operations to a protected hardware boundary, developers can focus on building their applications without worrying about accidental data leaks, insider threats, or malicious attempts to harvest credentials. The enclave becomes the ultimate gatekeeper: it controls how data flows and ensures that nothing escapes in plain form. User Auth Methods running inside Enclave A primary example is **user authentication**. All sign-in workflows, including email/password, OAuth, and upcoming passkey-based methods, are handled entirely within the enclave. As soon as a user's credentials enter our platform through the encrypted channel, they are routed straight into the protected environment, bypassing the host's operating system or any potential snooping channels. From there, authentication and session details remain in the enclave, ensuring that privileged outsiders cannot intercept or modify them. By centralizing these identity flows within a sealed environment, developers can assure their users that no one outside the enclave (including the cloud provider or the app's own sysadmins) can peek at, tamper with, or access sensitive login information. 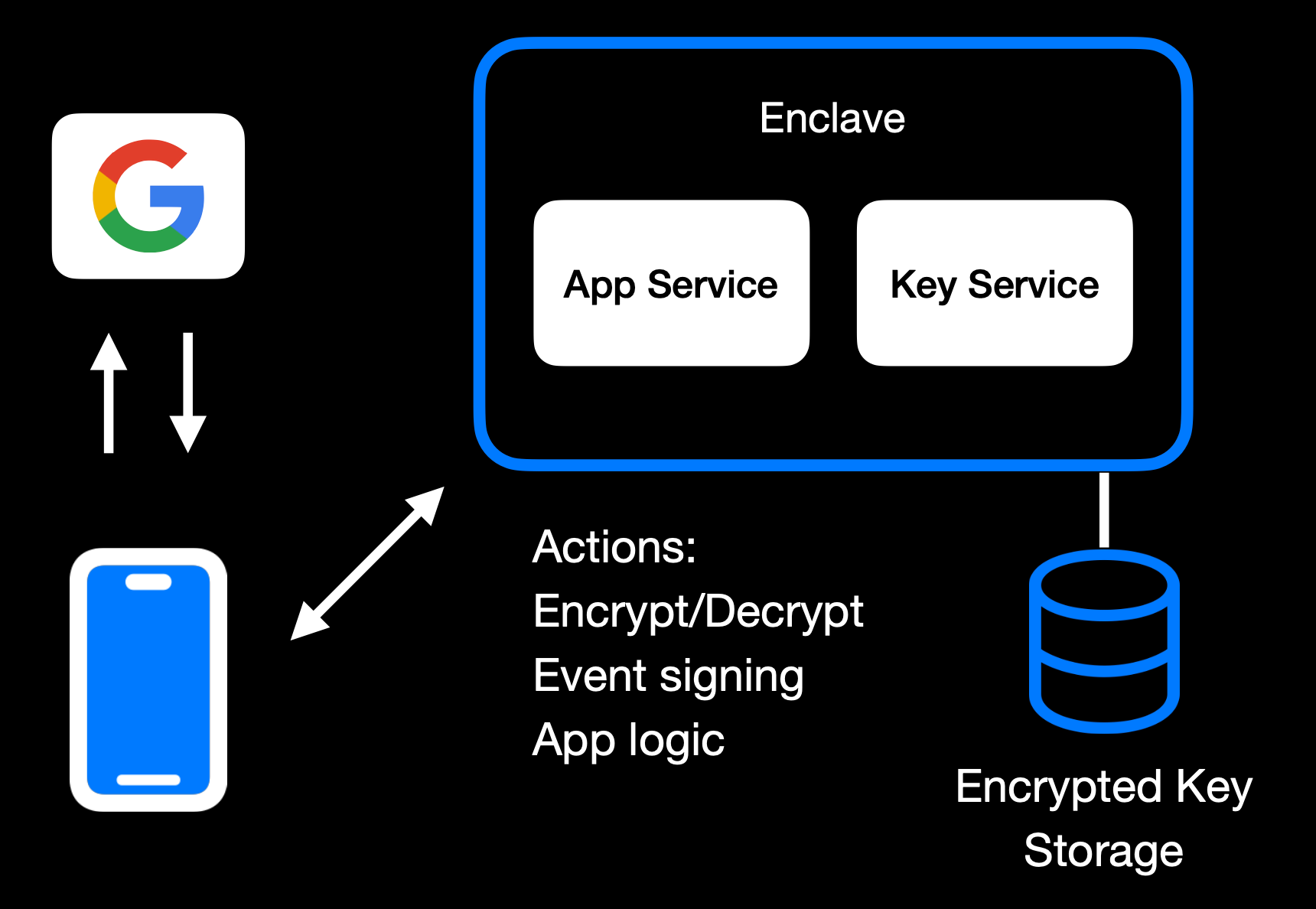Main Enclave Operations in OpenSecret The same principle applies to **private key management**. Whether keys are created fresh in the enclave or securely transferred into it, they remain sealed away from the rest of the system. Operations like digital signing or content decryption happen only within the hardware boundary, so raw keys never appear in any log, file system, or memory space outside the enclave. Developers retain the functionality they need, such as verifying user actions, encrypting data, or enabling secure transactions without ever exposing keys to a broader (and more vulnerable) attack surface. User backup options exist as well, where the keys can be securely passed to the end user. 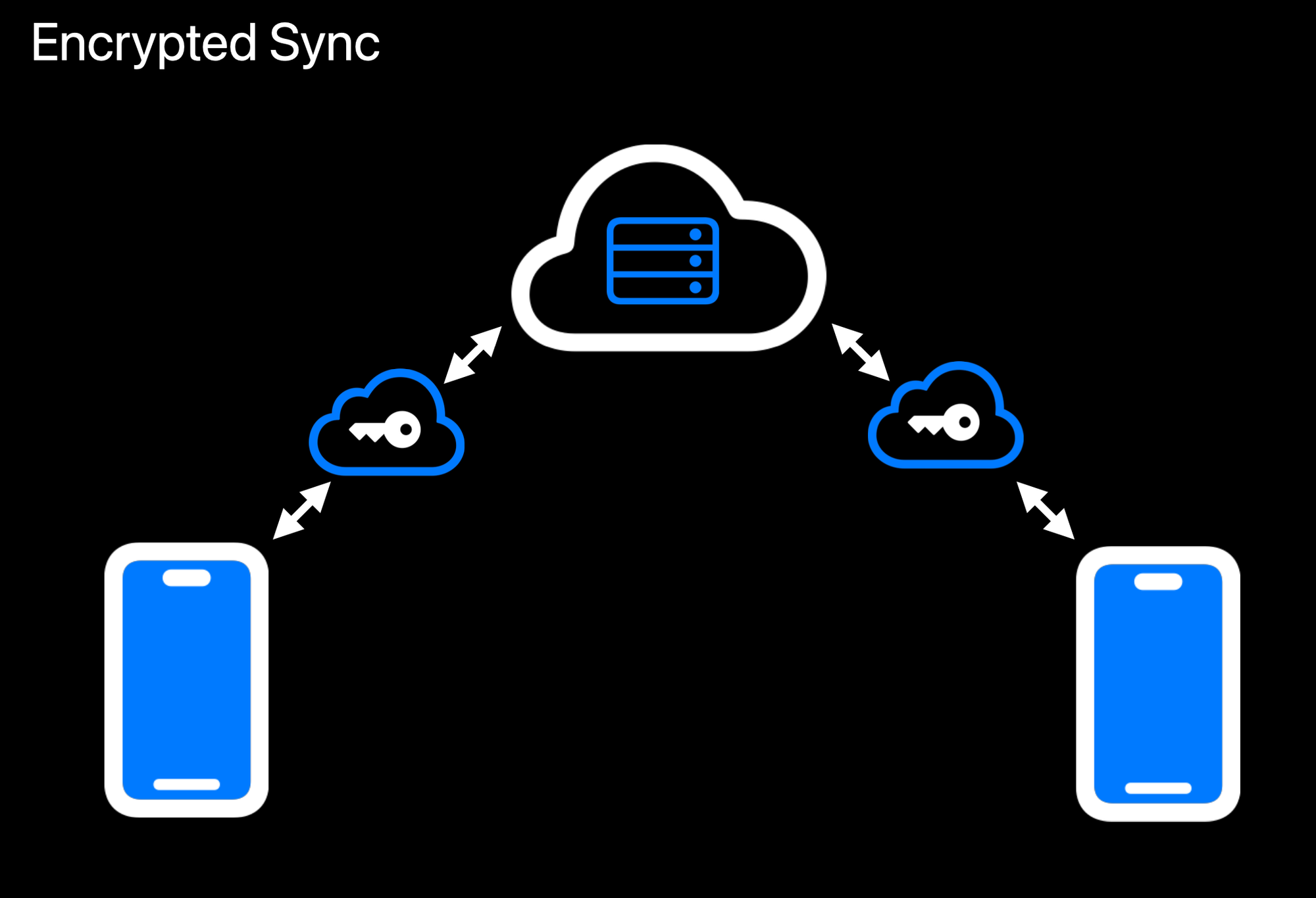Realtime Encrypted Data Sync on Multiple Devices Another crucial aspect is **data encryption at rest**. While user data ultimately needs to be stored somewhere outside the enclave, the unencrypted form of that data only exists transiently inside the protected environment. Encryption and decryption routines run within the enclave, which holds the encryption keys strictly in memory under hardware guards. If a user uploads data, it is promptly secured before it leaves the enclave. When data is retrieved, it remains encrypted until it reenters the protected region and is passed back to the user through the secured communication channel. This ensures that even if someone gains access to the underlying storage or intercepts data in transit, they will see only meaningless ciphertext. 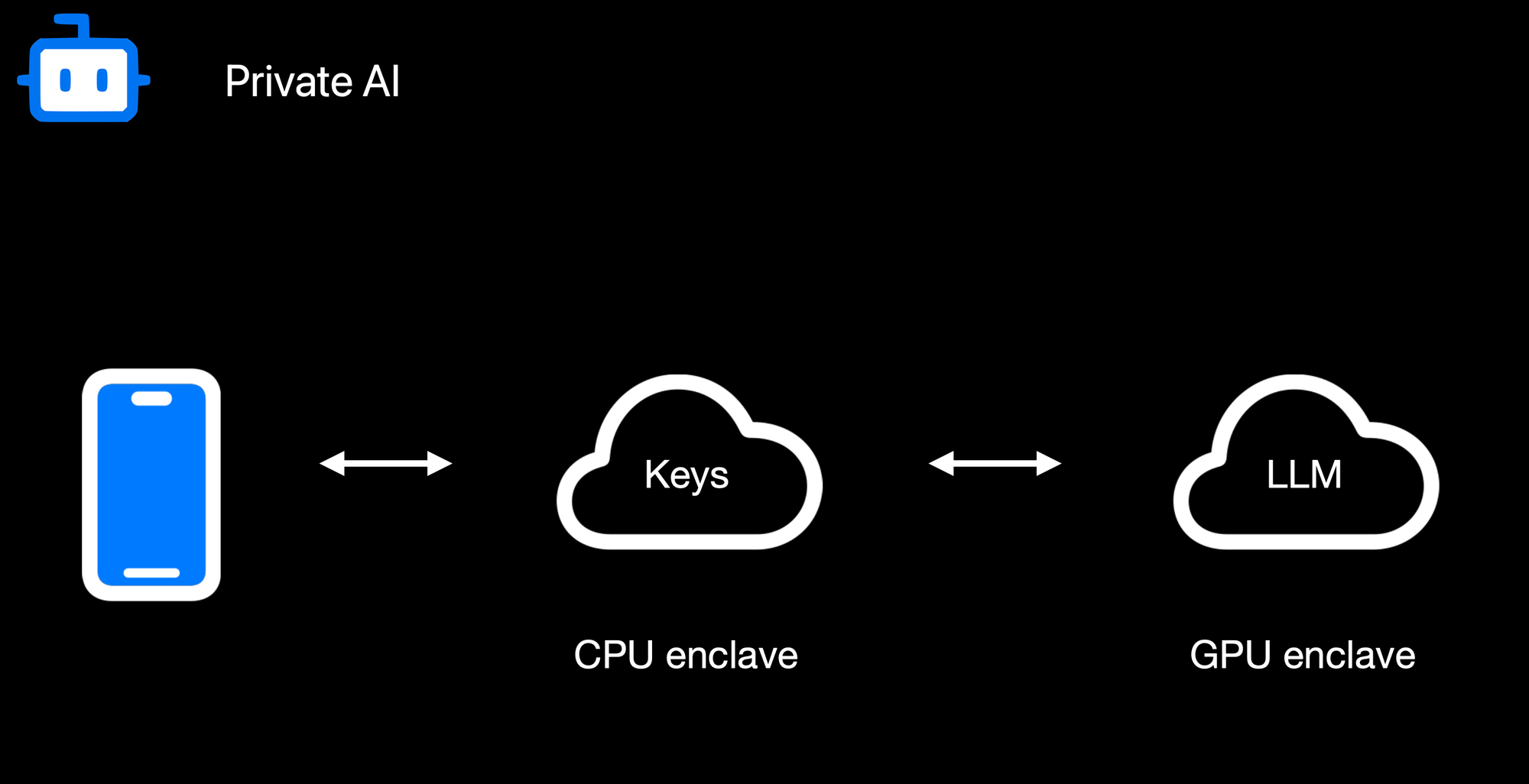Confidential AI Workloads Finally, **confidential AI workloads** build upon this same pattern: the Nitro enclave re-encrypts data so it can be processed inside a GPU-based trusted execution environment (TEE) for inference or other advanced computations. Sensitive data, like user-generated text or private documents, never appears in the clear on the host or within GPU memory outside the TEE boundary. When an AI process finishes, only the results are returned to the enclave, which can then relay them securely to the requesting user. By seamlessly chaining enclaves together, from CPU-based Nitro Enclaves to GPU-accelerated TEEs, we can deliver robust, hardware-enforced privacy for virtually any type of server-side or AI-driven operation. ### **Reproducible Builds + Verification** 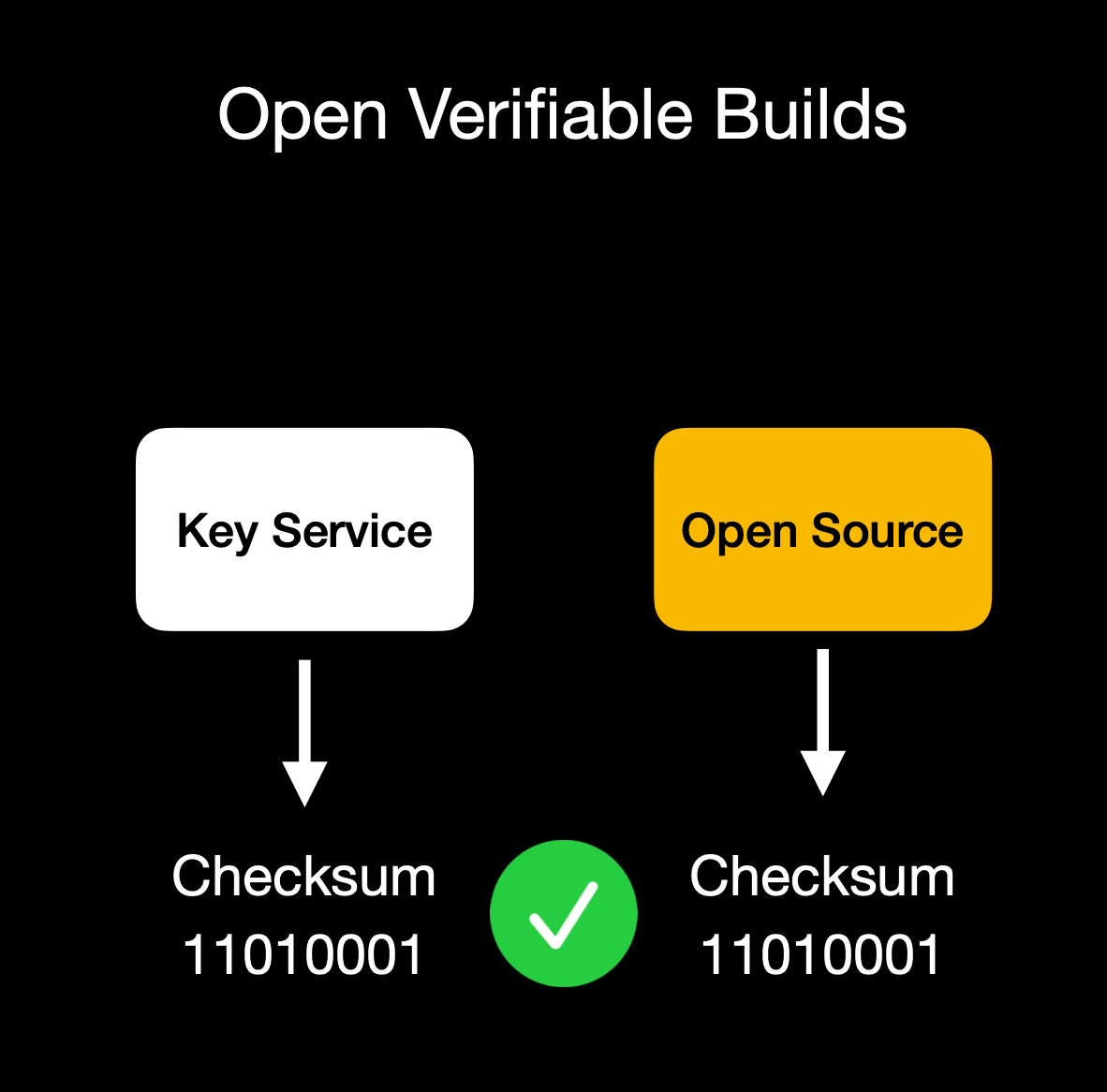Client verifies enclave attestation document We build our enclaves on **NixOS** with reproducible builds, ensuring that anyone can verify that the binary we publish is indeed the binary running in the enclave. This build process is essential for proving we haven't snuck in malicious code to exfiltrate data or collect sensitive logs. Our code is fully open source ([GitHub: OpenSecret](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud)), so you can audit or run it yourself. You can also verify that the cryptographic measurement the build process outputs matches the measurement reported by the enclave during attestation. ## **Putting It All Together** 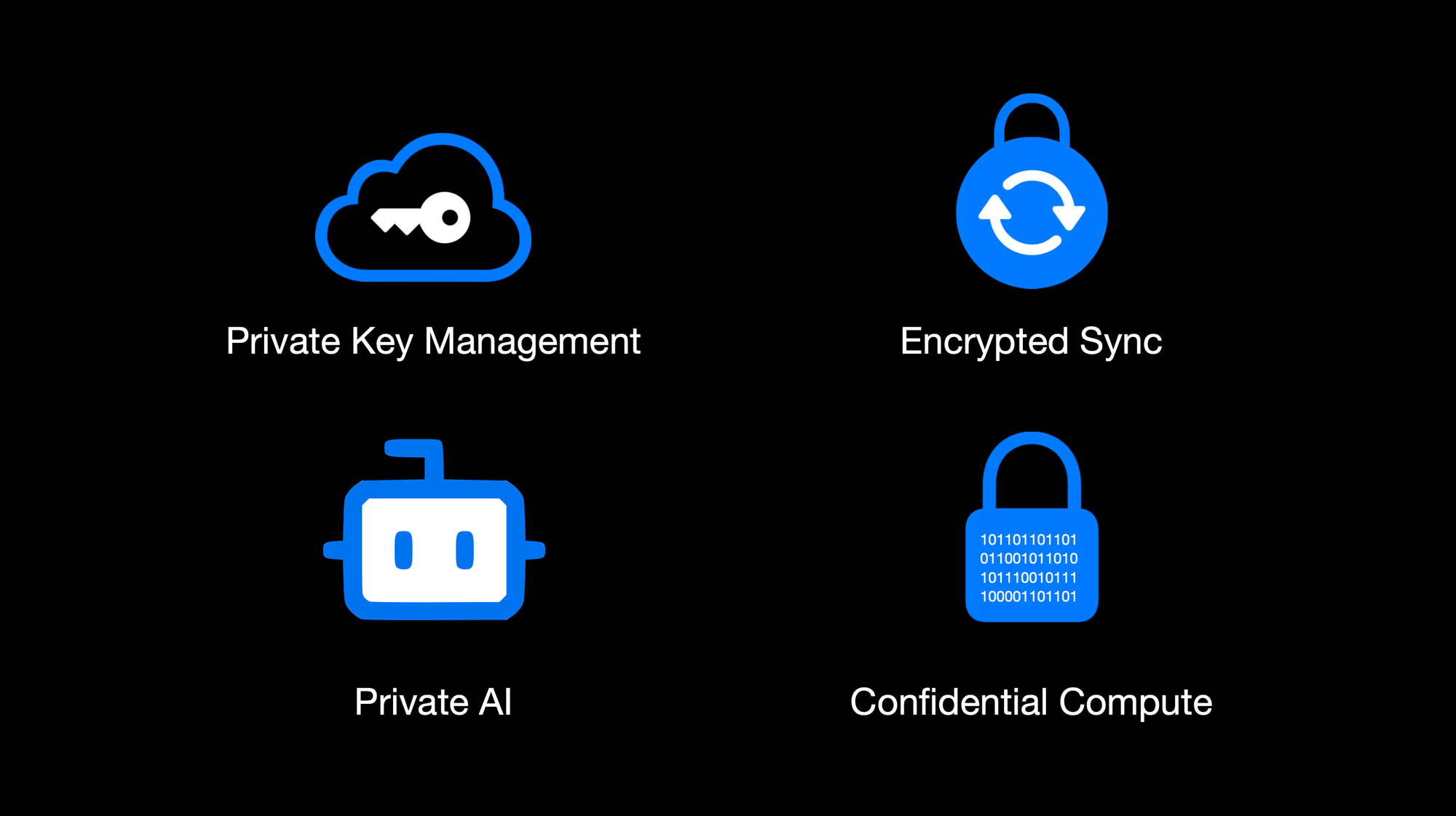OpenSecret Offering: Private Key Management, Encrypted Sync, Private AI, and Confidential Compute By weaving secure enclaves into every step, from authentication to data handling to AI inference, we shift the burden of trust away from human policies and onto provable, hardware-based protections. For app developers, you can offer your users robust privacy guarantees without rewriting all your business logic or building an entire security stack from scratch. Whether you're storing user credentials or running complex operations on sensitive data, the enclave approach ensures plaintext remains inaccessible to even the most privileged parties outside the enclave boundary. Developers can focus on building great apps, while OpenSecret handles the cryptographic "lock and key" behind the scenes. This model provides a secure-by-design environment for industries that demand strict data confidentiality, such as healthcare, fintech, cryptocurrency apps for secure key management, or decentralized identity platforms. Instead of worrying about memory dumps or backend tampering, you can trust that once data enters the enclave, it's sealed off from unauthorized eyes, including from the app developers themselves. And these safeguards don't just apply to niche use cases. Even general-purpose applications that handle login flows and user-generated content stand to benefit, especially as regulatory scrutiny grows around data privacy and insider threats. Imagine a telehealth startup using OpenSecret enclaves to protect patient information for remote consultations. Not only would patient data remain encrypted at rest, but any AI-driven analytics to assist with diagnoses could be run privately within the enclave, ensuring no one outside the hardware boundary can peek at sensitive health records. A fintech company could similarly isolate confidential financial transactions, preventing even privileged insiders from viewing or tampering with raw transaction details. These real-world implementations give developers a clear path to adopting enclaves for serious privacy and compliance needs without overhauling their infrastructure. OpenSecret aims to be a **full developer platform** with end-to-end security from day one. By incorporating user authentication, data storage, and GPU-based confidential AI into a single service, we eliminate many of the traditional hurdles in adopting enclaves. No more juggling separate tools for cryptographic key management, compliance controls, and runtime privacy. Instead, you get a unified stack that keeps data encrypted in transit, at rest, and in use. Our solution also caters to the exploding demand for AI applications: with TEE-enabled GPU workloads, you can securely process sensitive data for text inference without ever exposing raw plaintext or sensitive documents to the host system. The result is a new generation of apps that deliver advanced functionality, like real-time encrypted data sync or AI-driven insights, while preserving user privacy and meeting strict regulatory requirements. You don't have to rely on empty "trust us" promises because hardware enclaves, remote attestation, and reproducible builds collectively guarantee the code is running untampered. In short, OpenSecret offers the building blocks needed to create truly confidential services and experiences, allowing you to innovate while ensuring data protection remains ironclad. ## **Things to Come** We're excited to build on our enclaved approach. Here's what's on our roadmap: • **Production Launch**: We're using this in production now with [Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud) and have a developer preview playground up and running. We'll have the developer environment ready for production in a few months.\ • **Multi-Tenant Support**: Our platform currently works for single tenants, but we're opening this up so developers can onboard without needing a dedicated instance.\ • **Self-Serve Frontend**: A dev-friendly portal for provisioning apps, connecting OAuth or email providers, and managing users.\ • **External Key Signing Options**: Integrations with custom hardware security modules (HSMs) or customer-ran key managers that can only process data upon verifying the enclave attestation.\ • **Confidential Computing as a Service**: We'll expand our platform so that other developers can quickly create enclaves for specialized workloads without dealing with the complexities of Nitro or GPU TEEs.\ • **Additional SDKs**: In addition to our [JavaScript client-side SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud), we plan to launch official support for Rust, Python, Swift, Java, Go, and more.\ • **AI API Proxy with Attestation/Encryption**: We already provide an easy way to [access a Private AI through Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud), but we'd like to open this up more for existing tools and developers. We'll provide a proxy server that users can run on their local machines or servers that properly handle encryption to our OpenAI-compatible API. ## **Getting Started** Ready to see enclaves in action? Here's how to dive in:\ 1. **Run OpenSecret**: Check out our open-source repository at [OpenSecret on GitHub](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud). You can run your own enclaved environment or try it out locally with Docker.\ 2. **Review Our SDK**: Our [JavaScript client SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud) makes it easy to handle sign-ins, put/get encrypted data, sign with user private keys, etc. It handles attestation verification and encryption under the hood, making the API integration seamless.\ 3. **Play with Maple AI**: Try out [Maple AI](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) as an example of an AI app built directly on OpenSecret. Your queries are encrypted end to end, and the Llama model sees them only inside the TEE.\ 4. **Developer Preview**: Contact us if you want an invite to our early dev platform. We'll guide you through our SDK and give you access to the preview server. We'd love to build with you and incorporate your feedback as we develop this further. ## **Conclusion** By merging secure enclaves (AWS Nitro and Nvidia GPU TEEs), user authentication, private key management, and an end-to-end verifiable encrypted approach, **OpenSecret** provides a powerful platform where we protect user data during collection, storage, and processing. Whether it's for standard user management, handling private cryptographic keys, or powering AI inference, the technology ensures that **no one**, not even us or the cloud provider, can snoop on data in use. **We believe** this is the future of trustworthy computing in the cloud. And it's **all open source**, so you don't have to just take our word for it: you can see and verify everything yourself. Do you have questions, feedback, or a use case you'd like to test out? Come join us on [GitHub](https://github.com/OpenSecretCloud?ref=blog.opensecret.cloud), [Discord](https://discord.gg/ch2gjZAMGy?ref=blog.opensecret.cloud), or email us for a developer preview. We can't wait to see what you build! *Thank you for reading, and welcome to the era of enclaved computing.*
@ df173277:4ec96708
2025-02-07 00:41:34## **Building Our Confidential Backend on Secure Enclaves** With our newly released [private and confidential **Maple AI**](https://trymaple.ai/?ref=blog.opensecret.cloud) and the open sourcing of our [**OpenSecret** platform](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud) code, I'm excited to present this technical primer on how we built our confidential compute platform leveraging **secure enclaves**. By combining AWS Nitro enclaves with end-to-end encryption and reproducible builds, our platform gives developers and end users the confidence that user data is protected, even at runtime, and that the code operating on their data has not been tampered with. ## **Auth and Databases Today** As developers, we live in an era where protecting user data means "encryption at rest," plus some access policies and procedures. Developers typically run servers that: 1. Need to register users (authentication). 2. Collect and process user data in business-specific ways, often on the backend. Even if data is encrypted at rest, it's commonly unlocked with a single master key or credentials the server holds. This means that data is visible during runtime to the application, system administrators, and potentially to the hosting providers. This scenario makes it difficult (or impossible) to guarantee that sensitive data isn't snooped on, memory-dumped, or used in unauthorized ways (for instance, training AI models behind the scenes). ## **"Just Trust Us" Isn't Good Enough** In a traditional server architecture, users have to take it on faith that the code handling their data is the same code the operator claims to be running. Behind the scenes, applications can be modified or augmented to forward private information elsewhere, and there is no transparent way for users to verify otherwise. This lack of proof is unsettling, especially for services that process or store highly confidential data. Administrators, developers, or cloud providers with privileged access can inspect memory in plaintext, attach debuggers, or gain complete visibility into stored information. Hackers who compromise these privileged levels can directly access sensitive data. Even with strict policies or promises of good conduct, the reality is that technical capabilities and misconfigurations can override words on paper. If a server master key can decrypt your data or can be accessed by an insider with root permissions, then "just trust us" loses much of its credibility. The rise of AI platforms amplifies this dilemma. User data, often full of personal details, gets funneled into large-scale models that might be training or fine-tuning behind the scenes. Relying on vague assurances that "we don't look at your data" is no longer enough to prevent legitimate concerns about privacy and misuse. Now more than ever, providing a **strong, verifiable** guarantee that data remains off-limits, even when actively processed, has become a non-negotiable requirement for trustworthy services. ## **Current Attempts at Securing Data** 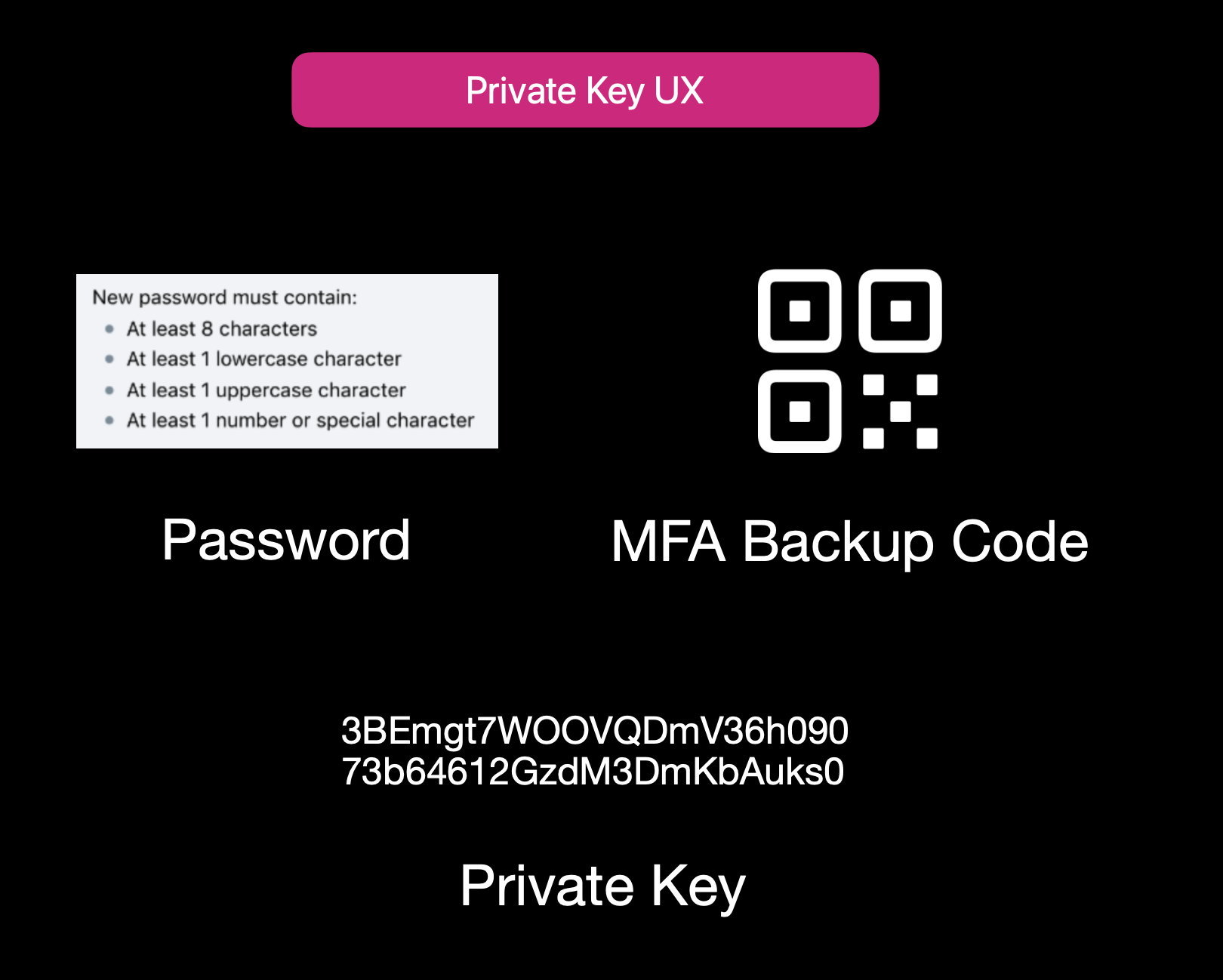Current User Experience of E2EE Apps While properly securing data is not easy, it isn't to say that no one is trying. Some solutions use **end-to-end encryption** (E2EE), where user data is encrypted client-side with a password or passphrase, so not even the server operator can decrypt it. That approach can be quite secure, but it also has its **limitations**: 1. **Key Management Nightmares**: If a user forgets their passphrase, the data is effectively lost, and there's no way to recover it from the developer's side. 2. **Feature Limitations**: Complex server-side operations (like offline/background tasks, AI queries, real-time collaboration, or heavy computation) can't easily happen if the server is never capable of processing decrypted data. 3. **Platform Silos**: Some solutions rely on iCloud, Google Drive, or local device storage. That can hamper multi-device usage or multi-OS compatibility. Other approaches include self-hosting. However, these either burden users with dev ops overhead or revert to the "trust me" model for the server if you "self-host" on a cloud provider. ## **Secure Enclaves** ### **The Hybrid Approach** Secure enclaves offer a compelling middle ground. They combine the privacy benefits of keeping data secure from prying admins while still allowing meaningful server-side computation. In a nutshell, an enclave is a protected environment within a machine, isolated at the hardware level, so that even if the OS or server is compromised, the data and code inside the enclave remain hidden. 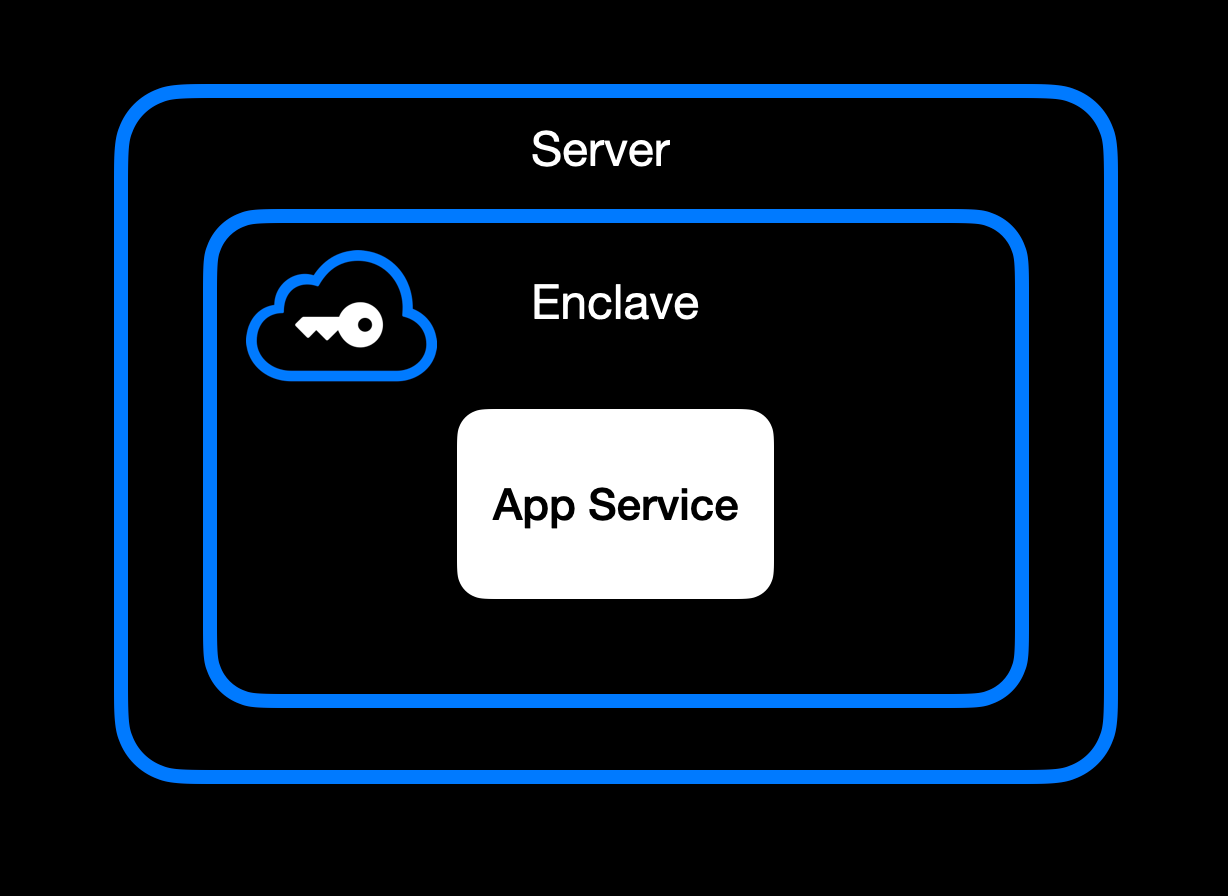App Service Running Inside Secure Enclave ### **High-Level Goal of Enclaves** Enclaves, also known under the broader umbrella of **confidential computing**, aim to:\ • **Lock down data** so that only authorized code within the enclave can process the original plaintext data.\ • **Deny external inspection** by memory dumping, attaching a debugger, or intercepting plaintext network traffic.\ • **Prove** to external users or services that an enclave is running unmodified, approved code (this is where **remote attestation** comes in). ### **Different Secure Enclave Solutions** [**AMD SEV**](https://www.amd.com/en/developer/sev.html?ref=blog.opensecret.cloud) **(Secure Encrypted Virtualization)** encrypts an entire virtual machine's memory so that even a compromised hypervisor cannot inspect or modify guest data. Its core concept is "lift-and-shift" security. No application refactoring is required because hardware-based encryption automatically protects the OS and all VM applications. Later enhancements (SEV-ES and SEV-SNP) added encryption of CPU register states and memory integrity protections, further limiting hypervisor tampering. This broad coverage means the guest OS is included in the trusted boundary. AMD SEV has matured into a robust solution for confidential VMs in multi-tenant clouds. [**Intel TDX**](https://www.intel.com/content/www/us/en/developer/tools/trust-domain-extensions/overview.html?ref=blog.opensecret.cloud) **(Trust Domain Extensions)** shifts from process-level enclaves to full VM encryption, allowing an entire guest operating system and its applications to run in an isolated "trust domain." Like AMD SEV, Intel TDX encrypts and protects all memory the VM uses from hypervisors or other privileged software, so developers do not need to refactor their code to benefit from hardware-based confidentiality. This broader scope addresses many SGX limitations, such as strict memory bounds and the need to split out enclave-specific logic, and offers a more straightforward "lift-and-shift" path for running existing workloads privately. While SGX is now deprecated, TDX carries forward the core confidential computing principles but applies them at the virtual machine level for more substantial isolation, easier deployment, and the ability to scale up to large, memory-intensive applications. [**Apple Secure Enclave and Private Compute**](https://security.apple.com/blog/private-cloud-compute/?ref=blog.opensecret.cloud) is a dedicated security coprocessor embedded in most Apple devices (iPhones, iPads, Macs) and now extended to Apple's server-side AI infrastructure. It runs its own microkernel, has hardware-protected memory, and securely manages operations such as biometric authentication, key storage, and cryptographic tasks. Apple's "Private Compute" approach in the cloud brings similar enclave capabilities to server-based AI, enabling on-device-grade privacy even when requests are processed in Apple's data centers. [**AWS Nitro Enclaves**](https://docs.aws.amazon.com/enclaves/latest/user/nitro-enclave.html?ref=blog.opensecret.cloud) carve out a tightly isolated "mini-VM" from a parent EC2 instance, with its own vCPUs and memory guarded by dedicated Nitro cards. The enclave has no persistent storage and no external network access, significantly reducing the attack surface. Communication with the parent instance occurs over a secure local channel (vsock), and AWS offers hardware-based attestation so that secrets (e.g., encryption keys from AWS KMS) can be accessed only to the correct enclave. This design helps developers protect sensitive data or code even if the main EC2 instance's OS is compromised. [**NVIDIA GPU TEEs**](https://www.nvidia.com/en-us/data-center/solutions/confidential-computing/?ref=blog.opensecret.cloud) **(Hopper H100 and Blackwell)** extend confidential computing to accelerated workloads by encrypting data in GPU memory and ensuring that even a privileged host cannot view or tamper with it. Data moving between CPU and GPU is encrypted in transit, so sensitive model weights or inputs remain protected during AI training or inference. NVIDIA's hardware and drivers handle secure data paths under the hood, allowing confidential large language model (LLM) workloads and other GPU-accelerated computations to run with minimal performance overhead and strong security guarantees. ### **Key Benefits** One major advantage of enclaves is their ability to **keep memory completely off-limits** to outside prying eyes. Even administrators who can normally inspect processes at will are blocked from peeking into the enclave's protected memory space. The enclave model is a huge shift in the security model: it prevents casual inspection and defends against sophisticated memory dumping techniques that might otherwise leak secrets or sensitive data. Another key benefit centers on cryptographic keys that are **never exposed outside the enclave**. Only verified code running inside the enclave environment can run decryption or signing operations, and it can only do so while that specific code is running. This ensures that compromised hosts or rogue processes, even those with high-level privileges, are unable to intercept or misuse the keys because the keys remain strictly within the trusted boundary of the hardware. Enclaves can also offer the power of **remote attestation**, allowing external clients or systems to confirm that they're speaking to an authentic, untampered enclave. By validating the hardware's integrity measurements and enclave-specific proofs, the remote party can be confident in the underlying security properties, an important guarantee in multi-tenant environments or whenever trust boundaries extend across different organizations and networks. Beyond that, **reproducible builds** can create a verifiable fingerprint proving which binary runs in the enclave. This is a step above a simple "trust us" approach. Anyone can independently recreate the enclave image and verify the resulting cryptographic hash by using a reproducible build system (for example, [our NixOS-based solution](https://github.com/OpenSecretCloud/opensecret/blob/master/flake.nix?ref=blog.opensecret.cloud)). If it matches, then users and developers know precisely how code handles their data, boosting confidence that no hidden changes exist. It's worth noting that although enclaves shield you from software devs, cloud providers, and insider threats, you do have to trust the **hardware vendor** (Intel, AMD, Apple, AWS, or NVIDIA) to implement their microcode and firmware securely. The entire enclave model could be theoretically undermined if a CPU maker's root keys or manufacturing process were compromised. Fortunately, these companies undergo extensive audits and firmware validations (often with third-party researchers), and their remote attestation mechanisms allow you to confirm specific firmware versions before trusting an enclave. While this adds a layer of "vendor trust," it's still a far more contained risk than trusting an entire operating system or cloud stack, so enclaves remain a strong step forward in practical, confidential computing. ## **How We Use Secure Enclaves** Now that we've covered the general idea of enclaves let's look at how we specifically implement them in OpenSecret, our developer platform for handling user auth, private keys, data encryption, and AI workloads. ### **Our Stack: AWS Nitro + Nvidia TEE** • **AWS Nitro Enclaves for the backend**: All critical logic, authentication, private key management, and data encryption/decryption run inside an AWS Nitro Enclave. • **Nvidia Trusted Execution for AI**: For large AI inference (such as the Llama 3.3 70B model), we utilize Nvidia's GPU-based TEEs to protect even GPU memory. This means users can feed sensitive data to the AI model **without** exposing it in plaintext to the GPU providers or us as the operator. [Edgeless Systems](https://www.edgeless.systems/?ref=blog.opensecret.cloud) is our Nvidia TEE provider, and due to the power of enclave verification, we don't need to worry about who runs the GPUs. We know requests can't be inspected or tampered with. ### **End-to-End Encryption from Client to Enclave** 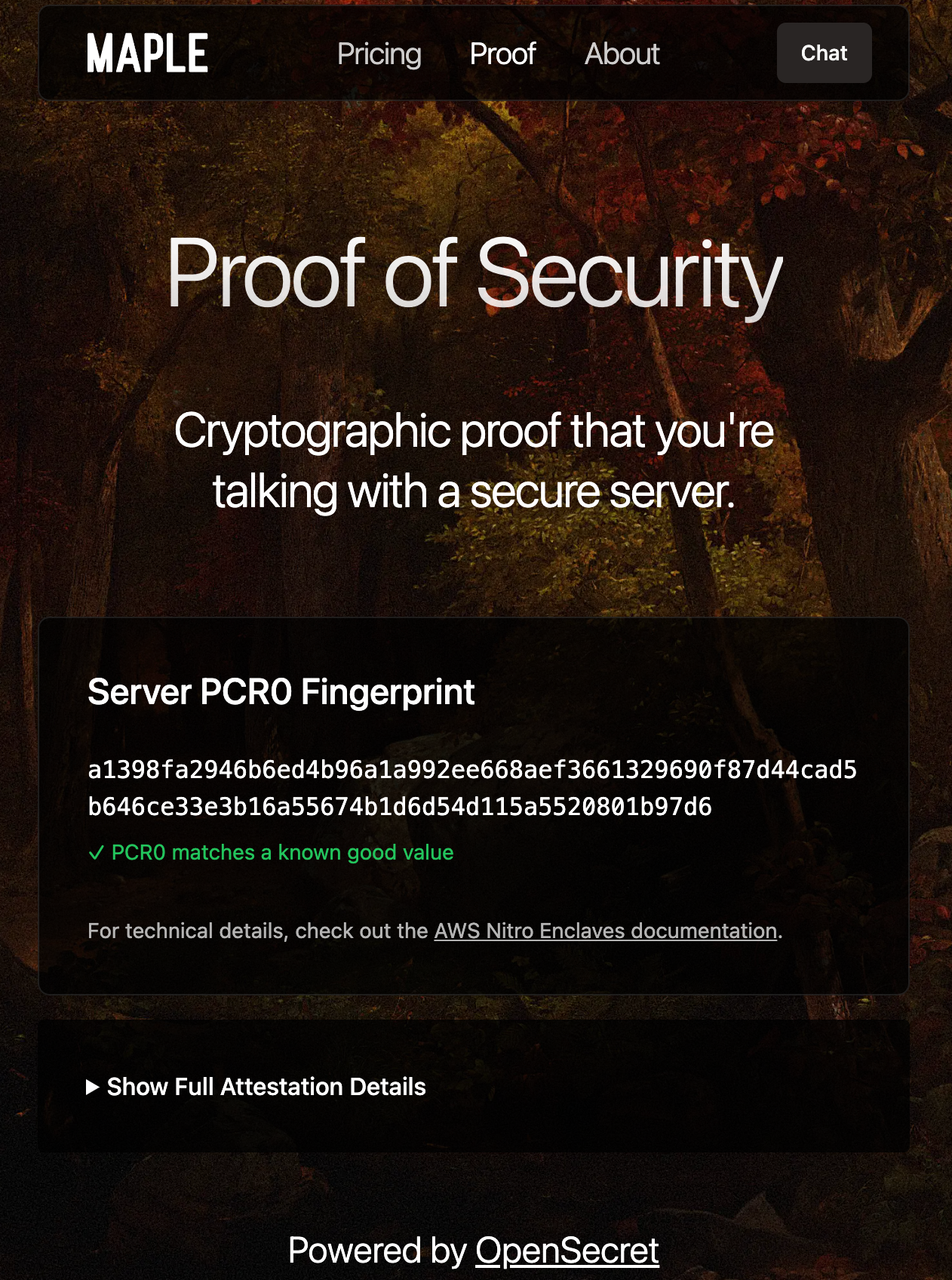Client-side Enclave Attestation from Maple AI Before login or data upload, the user/client verifies the **enclave attestation** from our platform. This process proves that the specific Nitro Enclave is genuine and runs the exact code we've published. You can check this out live on [Maple AI's attestation page](https://trymaple.ai/proof?ref=blog.opensecret.cloud). Based on the attestation, the client establishes a secure ephemeral communication channel that only that enclave can decrypt. While we take advantage of SSL, it is typically not terminated inside the enclave itself. To ensure there's full encrypted data transfer all the way through to the enclave, we establish this additional handshake based on the attestation document that is used for all API requests during the client session. From there, the user's credentials, private keys, and data pass through this secure channel directly into the enclave, where they are decrypted and processed according to the user's request. ### **In-Enclave Operations** At the core of OpenSecret's approach is the conviction that security-critical tasks must happen inside the enclave, where even administrative privileges or hypervisor-level compromise cannot expose plaintext data. This encompasses everything from when a user logs in to creating and managing sensitive cryptographic keys. By confining these operations to a protected hardware boundary, developers can focus on building their applications without worrying about accidental data leaks, insider threats, or malicious attempts to harvest credentials. The enclave becomes the ultimate gatekeeper: it controls how data flows and ensures that nothing escapes in plain form. User Auth Methods running inside Enclave A primary example is **user authentication**. All sign-in workflows, including email/password, OAuth, and upcoming passkey-based methods, are handled entirely within the enclave. As soon as a user's credentials enter our platform through the encrypted channel, they are routed straight into the protected environment, bypassing the host's operating system or any potential snooping channels. From there, authentication and session details remain in the enclave, ensuring that privileged outsiders cannot intercept or modify them. By centralizing these identity flows within a sealed environment, developers can assure their users that no one outside the enclave (including the cloud provider or the app's own sysadmins) can peek at, tamper with, or access sensitive login information. 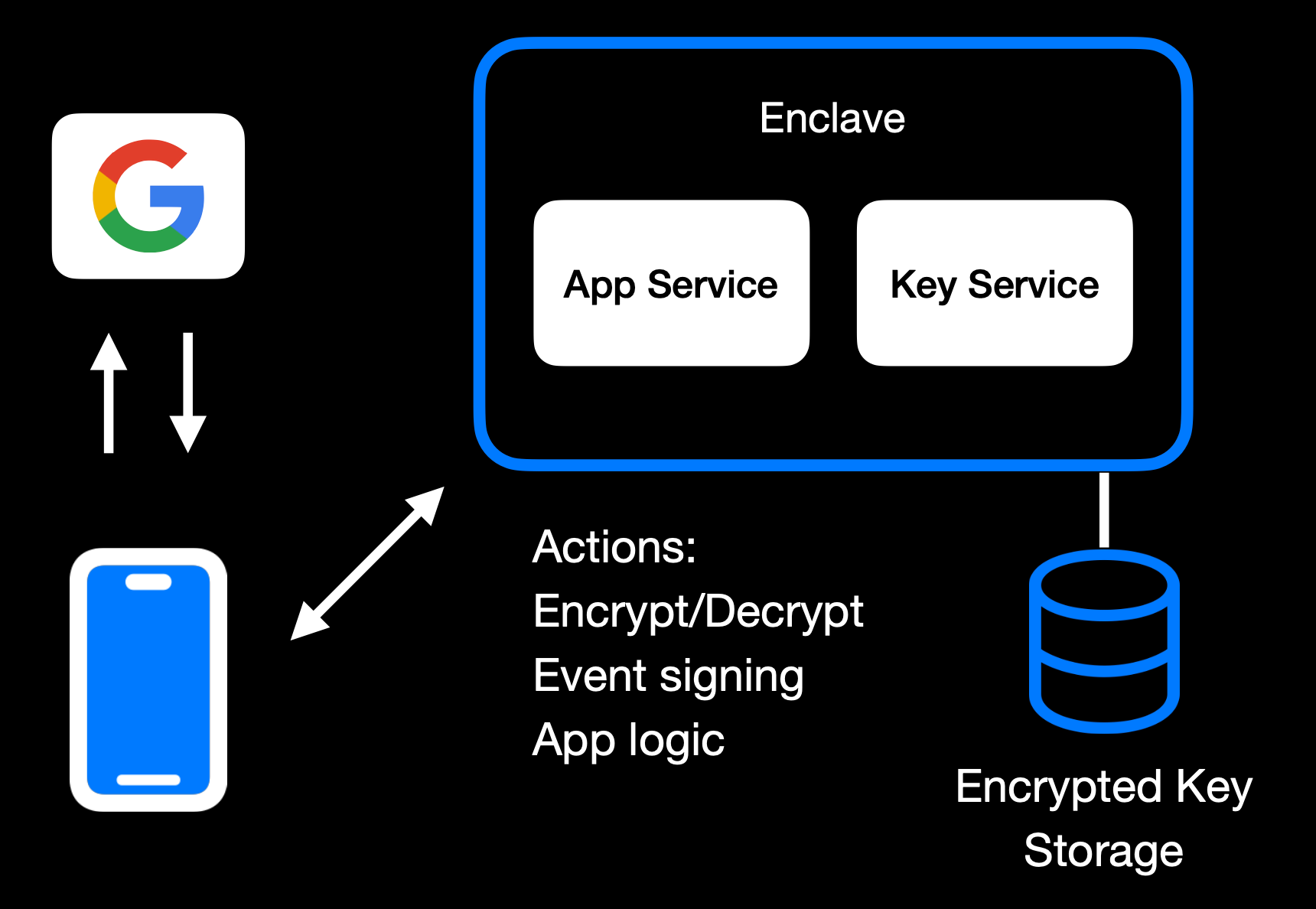Main Enclave Operations in OpenSecret The same principle applies to **private key management**. Whether keys are created fresh in the enclave or securely transferred into it, they remain sealed away from the rest of the system. Operations like digital signing or content decryption happen only within the hardware boundary, so raw keys never appear in any log, file system, or memory space outside the enclave. Developers retain the functionality they need, such as verifying user actions, encrypting data, or enabling secure transactions without ever exposing keys to a broader (and more vulnerable) attack surface. User backup options exist as well, where the keys can be securely passed to the end user. 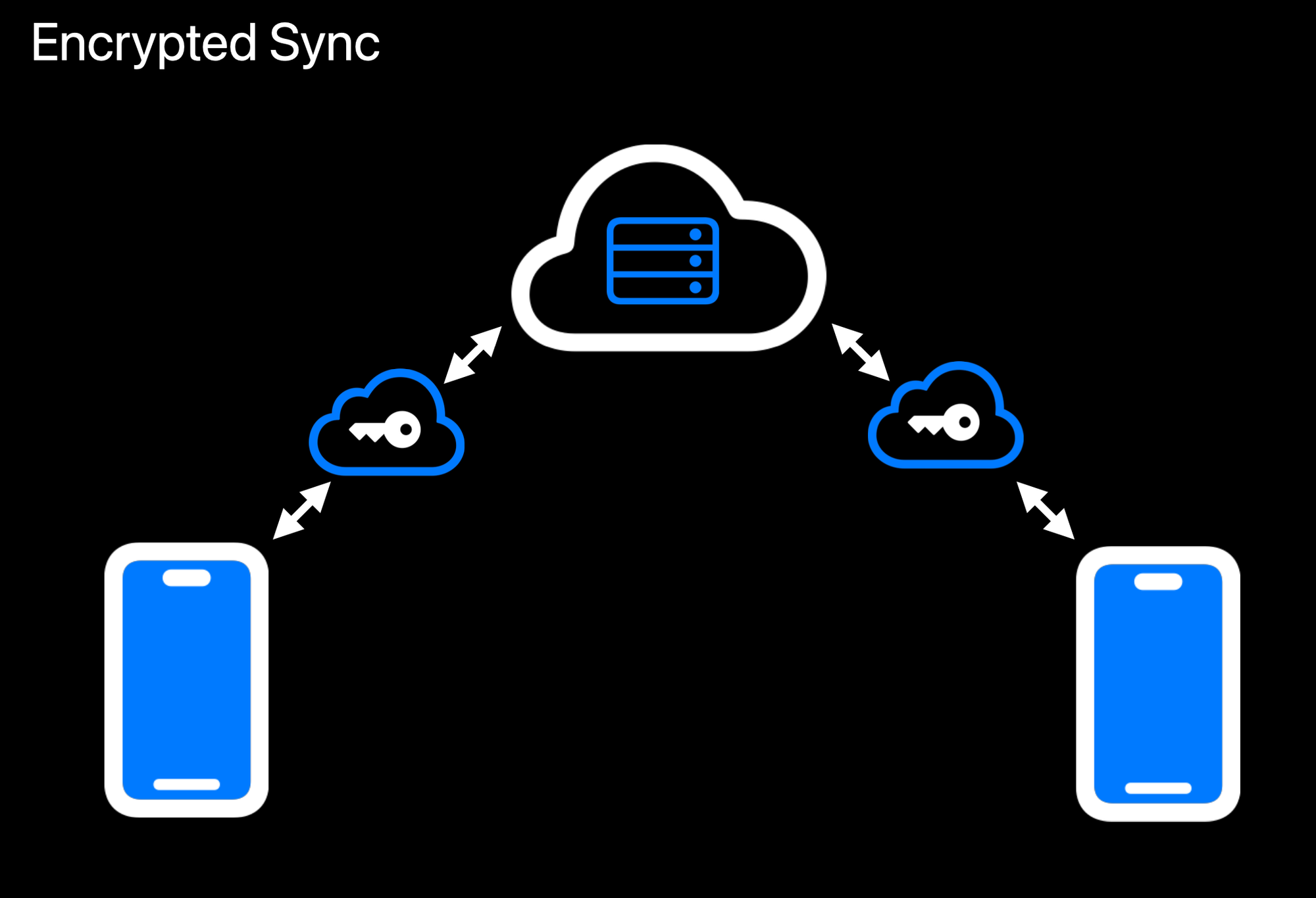Realtime Encrypted Data Sync on Multiple Devices Another crucial aspect is **data encryption at rest**. While user data ultimately needs to be stored somewhere outside the enclave, the unencrypted form of that data only exists transiently inside the protected environment. Encryption and decryption routines run within the enclave, which holds the encryption keys strictly in memory under hardware guards. If a user uploads data, it is promptly secured before it leaves the enclave. When data is retrieved, it remains encrypted until it reenters the protected region and is passed back to the user through the secured communication channel. This ensures that even if someone gains access to the underlying storage or intercepts data in transit, they will see only meaningless ciphertext. 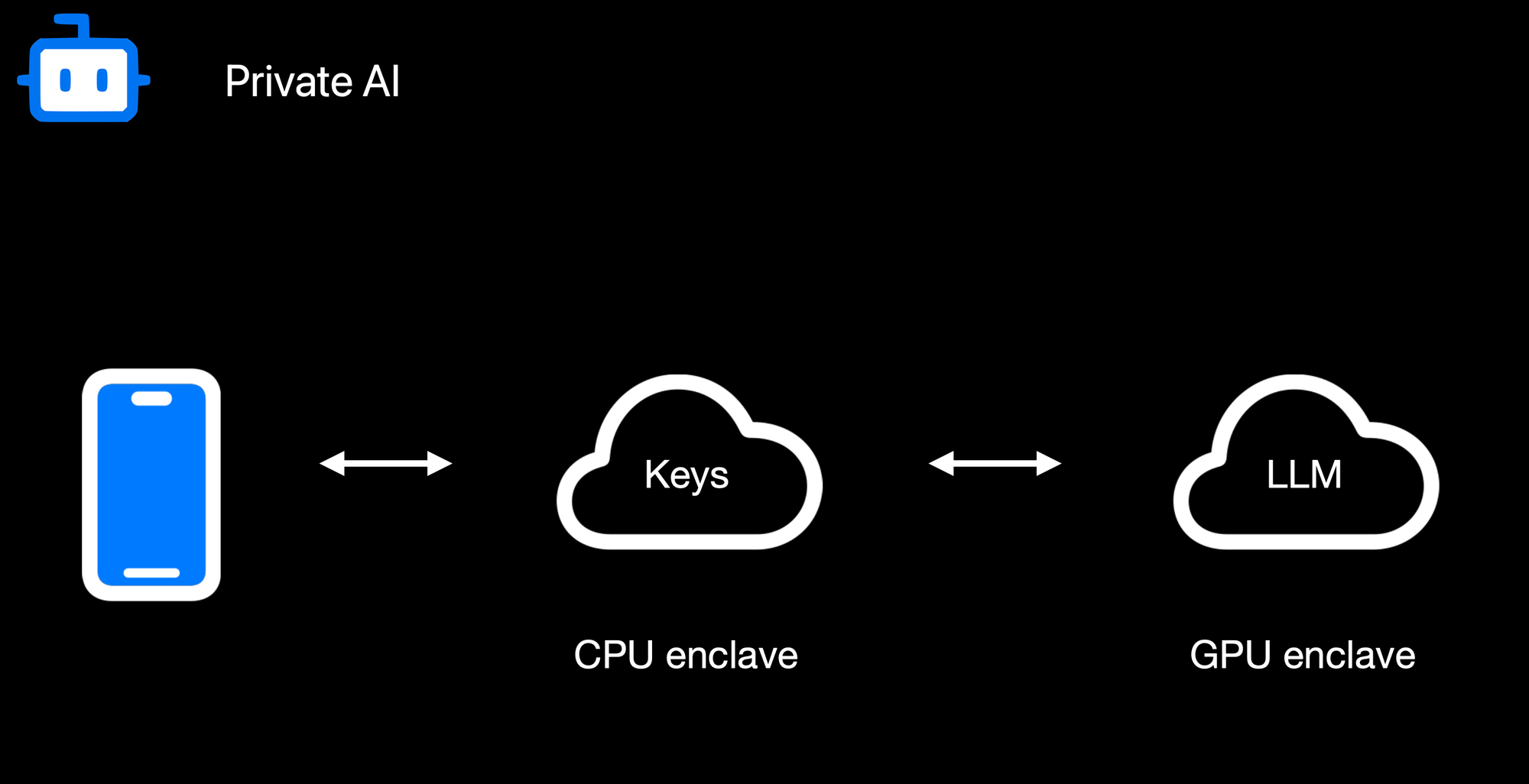Confidential AI Workloads Finally, **confidential AI workloads** build upon this same pattern: the Nitro enclave re-encrypts data so it can be processed inside a GPU-based trusted execution environment (TEE) for inference or other advanced computations. Sensitive data, like user-generated text or private documents, never appears in the clear on the host or within GPU memory outside the TEE boundary. When an AI process finishes, only the results are returned to the enclave, which can then relay them securely to the requesting user. By seamlessly chaining enclaves together, from CPU-based Nitro Enclaves to GPU-accelerated TEEs, we can deliver robust, hardware-enforced privacy for virtually any type of server-side or AI-driven operation. ### **Reproducible Builds + Verification** 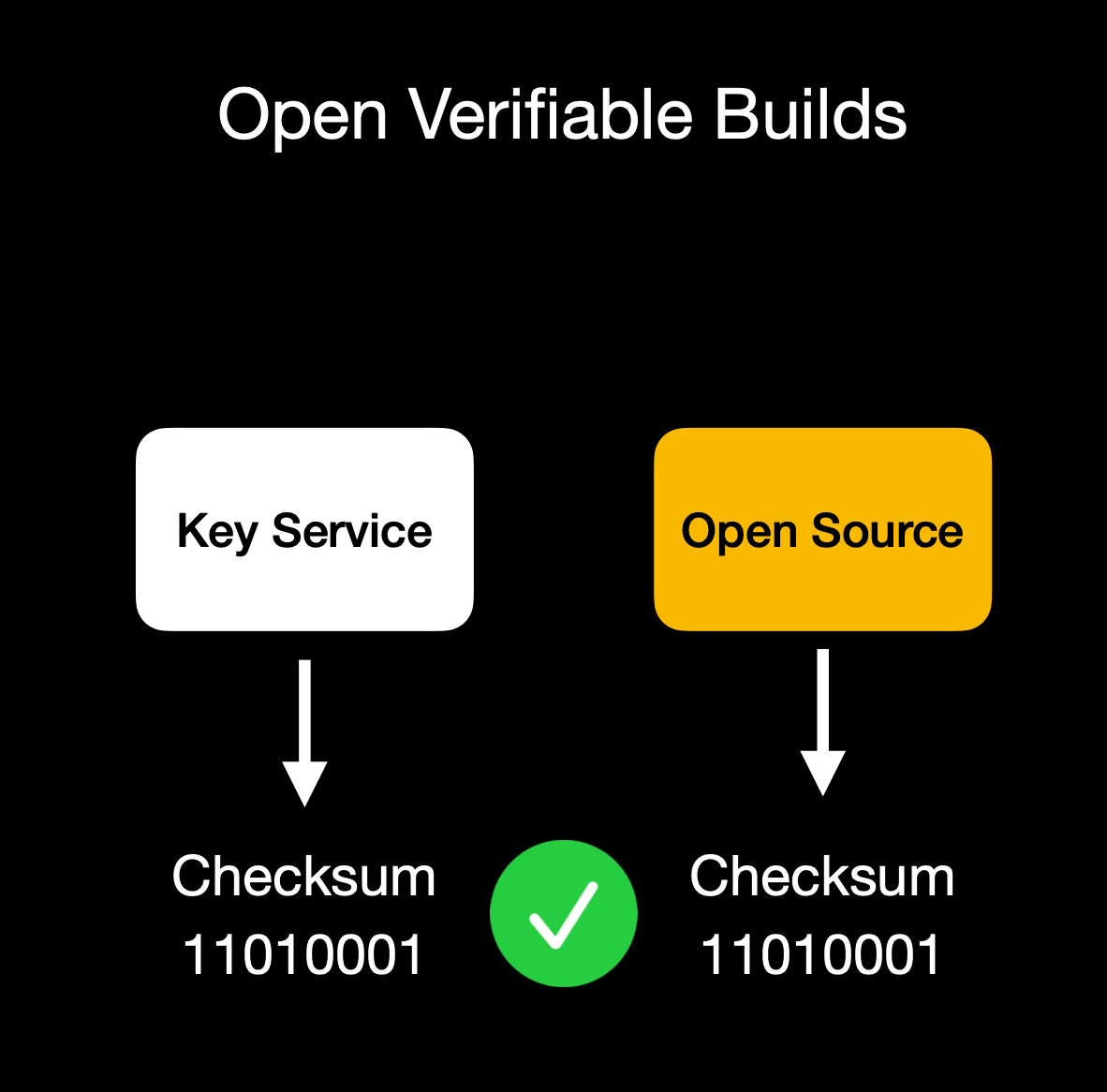Client verifies enclave attestation document We build our enclaves on **NixOS** with reproducible builds, ensuring that anyone can verify that the binary we publish is indeed the binary running in the enclave. This build process is essential for proving we haven't snuck in malicious code to exfiltrate data or collect sensitive logs. Our code is fully open source ([GitHub: OpenSecret](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud)), so you can audit or run it yourself. You can also verify that the cryptographic measurement the build process outputs matches the measurement reported by the enclave during attestation. ## **Putting It All Together** OpenSecret Offering: Private Key Management, Encrypted Sync, Private AI, and Confidential Compute By weaving secure enclaves into every step, from authentication to data handling to AI inference, we shift the burden of trust away from human policies and onto provable, hardware-based protections. For app developers, you can offer your users robust privacy guarantees without rewriting all your business logic or building an entire security stack from scratch. Whether you're storing user credentials or running complex operations on sensitive data, the enclave approach ensures plaintext remains inaccessible to even the most privileged parties outside the enclave boundary. Developers can focus on building great apps, while OpenSecret handles the cryptographic "lock and key" behind the scenes. This model provides a secure-by-design environment for industries that demand strict data confidentiality, such as healthcare, fintech, cryptocurrency apps for secure key management, or decentralized identity platforms. Instead of worrying about memory dumps or backend tampering, you can trust that once data enters the enclave, it's sealed off from unauthorized eyes, including from the app developers themselves. And these safeguards don't just apply to niche use cases. Even general-purpose applications that handle login flows and user-generated content stand to benefit, especially as regulatory scrutiny grows around data privacy and insider threats. Imagine a telehealth startup using OpenSecret enclaves to protect patient information for remote consultations. Not only would patient data remain encrypted at rest, but any AI-driven analytics to assist with diagnoses could be run privately within the enclave, ensuring no one outside the hardware boundary can peek at sensitive health records. A fintech company could similarly isolate confidential financial transactions, preventing even privileged insiders from viewing or tampering with raw transaction details. These real-world implementations give developers a clear path to adopting enclaves for serious privacy and compliance needs without overhauling their infrastructure. OpenSecret aims to be a **full developer platform** with end-to-end security from day one. By incorporating user authentication, data storage, and GPU-based confidential AI into a single service, we eliminate many of the traditional hurdles in adopting enclaves. No more juggling separate tools for cryptographic key management, compliance controls, and runtime privacy. Instead, you get a unified stack that keeps data encrypted in transit, at rest, and in use. Our solution also caters to the exploding demand for AI applications: with TEE-enabled GPU workloads, you can securely process sensitive data for text inference without ever exposing raw plaintext or sensitive documents to the host system. The result is a new generation of apps that deliver advanced functionality, like real-time encrypted data sync or AI-driven insights, while preserving user privacy and meeting strict regulatory requirements. You don't have to rely on empty "trust us" promises because hardware enclaves, remote attestation, and reproducible builds collectively guarantee the code is running untampered. In short, OpenSecret offers the building blocks needed to create truly confidential services and experiences, allowing you to innovate while ensuring data protection remains ironclad. ## **Things to Come** We're excited to build on our enclaved approach. Here's what's on our roadmap: • **Production Launch**: We're using this in production now with [Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud) and have a developer preview playground up and running. We'll have the developer environment ready for production in a few months.\ • **Multi-Tenant Support**: Our platform currently works for single tenants, but we're opening this up so developers can onboard without needing a dedicated instance.\ • **Self-Serve Frontend**: A dev-friendly portal for provisioning apps, connecting OAuth or email providers, and managing users.\ • **External Key Signing Options**: Integrations with custom hardware security modules (HSMs) or customer-ran key managers that can only process data upon verifying the enclave attestation.\ • **Confidential Computing as a Service**: We'll expand our platform so that other developers can quickly create enclaves for specialized workloads without dealing with the complexities of Nitro or GPU TEEs.\ • **Additional SDKs**: In addition to our [JavaScript client-side SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud), we plan to launch official support for Rust, Python, Swift, Java, Go, and more.\ • **AI API Proxy with Attestation/Encryption**: We already provide an easy way to [access a Private AI through Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud), but we'd like to open this up more for existing tools and developers. We'll provide a proxy server that users can run on their local machines or servers that properly handle encryption to our OpenAI-compatible API. ## **Getting Started** Ready to see enclaves in action? Here's how to dive in:\ 1. **Run OpenSecret**: Check out our open-source repository at [OpenSecret on GitHub](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud). You can run your own enclaved environment or try it out locally with Docker.\ 2. **Review Our SDK**: Our [JavaScript client SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud) makes it easy to handle sign-ins, put/get encrypted data, sign with user private keys, etc. It handles attestation verification and encryption under the hood, making the API integration seamless.\ 3. **Play with Maple AI**: Try out [Maple AI](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) as an example of an AI app built directly on OpenSecret. Your queries are encrypted end to end, and the Llama model sees them only inside the TEE.\ 4. **Developer Preview**: Contact us if you want an invite to our early dev platform. We'll guide you through our SDK and give you access to the preview server. We'd love to build with you and incorporate your feedback as we develop this further. ## **Conclusion** By merging secure enclaves (AWS Nitro and Nvidia GPU TEEs), user authentication, private key management, and an end-to-end verifiable encrypted approach, **OpenSecret** provides a powerful platform where we protect user data during collection, storage, and processing. Whether it's for standard user management, handling private cryptographic keys, or powering AI inference, the technology ensures that **no one**, not even us or the cloud provider, can snoop on data in use. **We believe** this is the future of trustworthy computing in the cloud. And it's **all open source**, so you don't have to just take our word for it: you can see and verify everything yourself. Do you have questions, feedback, or a use case you'd like to test out? Come join us on [GitHub](https://github.com/OpenSecretCloud?ref=blog.opensecret.cloud), [Discord](https://discord.gg/ch2gjZAMGy?ref=blog.opensecret.cloud), or email us for a developer preview. We can't wait to see what you build! *Thank you for reading, and welcome to the era of enclaved computing.* @ 04cb16e4:2ec3e5d5
2025-04-02 10:51:31Wenn irgendein weltpolitisches Thema auf den Tisch kommt, wird zumeist erst einmal gefragt, ob du dafür oder dagegen bist und auf welcher Seite du dich befindest. Das macht es einfacher, dich als Freund oder Feind einzusortieren. So wird das Leben übersichtlicher und man muss nicht in die Tiefe gehen und sich mit lästigen Details auseinandersetzen. Man muss auch nicht verreisen um sich ein Bild zu machen. Dafür gibt es ja die Tagesschau. Klassisches Beispiel: Ich war vor Kurzem mit einigen Freunden essen. Einer berichtete entsetzt: „Der Putin hat die Heimatstadt von Selenski angegriffen!“  Ich versuchte mir das bildlich vorzustellen und kam zu dem Schluss, das „der Putin“ wahrscheinlich Verstärkung dabei hatte. Und ausgerechnet nachdem Trump und dessen Flügelmann Vance den armen Wolodymyr rund gemacht hatten, greift der böse Imperator dessen Heimatstadt an. Das ist fies! Das macht „der Putin“ wahrscheinlich immer so, wenn er jemandem eins auswischen will. Die Heimatstadt angreifen! Ganz gleich, ob es strategisch gerade Sinn macht oder nicht. "Der Putin" ist halt ein Teufel. [Telegramkanal RBM](https://t.me/radio_berliner_morgenroete_de) [Radio Berliner Morgenröte auf X](https://x.com/RBM_Schindler) Ich denke viele gucken einfach zu viele qualitativ minderwertige Spielfilme und können Fiktion und Realität nicht mehr voneinander unterscheiden. Möglicherweise meinen sie auch, weil sie die Handlung eines Kriegsfilmes gerafft haben, verstehen sie einen Krieg. <https://www.eisbrenner.de/produkt-kategorie/buch/> <https://befreiung.org/> Mein Gesprächspartner Tino Eisbrenner hat keine Sightseeing Tour durch Moskau gemacht, sondern ist in Land und Leute regelrecht eingetaucht. Außerdem kommt seine Schwiegermutter aus Russland. Da ist man dem ganzen auch menschlich viel näher und bekommt man ganz andere Einblicke als die, die einem von der Tagesschau gewährt werden. Tino ist als Friedensmusiker viel im Osten unterwegs, unter anderem auch in Georgien, Weißrussland und auf der Krim. Er spricht mit Politikern, Künstlern, Journalisten, Taxifahrern und Dissidenten. Und viele fragen ihn: „Was ist eigentlich mit den Deutschen los?“ Gute Frage! Was ist eigentlich mit uns los? Wir senden unsere Volksvertreter in die Welt hinaus, damit sie Staatsoberhäuptern aus Ländern - die um ein Vielfaches umfangreicher an Fläche und Einwohnerzahl sind und eine komplett andere Kulturgeschichte haben - damit sie denen erklären können wie man seinen Job macht. Wahrscheinlich in dem irrwitzigen Glauben, dass sie selbst ihren Job tadellos und vorbildlich ausführen. **Spenden nehmen wir entweder mit dem Paypal Button am Ende** **[unserer Webseite](https://radio-berliner-morgenroete.de/)** **<https://radio-berliner-morgenroete.de/>** **oder per Überweisung aufs Bankkonto: DE93 1001 1001 2624 3740 74 entgegen.** Wir sind aber nicht nur verantwortlich für unsere politische Führung, sondern auch für unseren Umgang miteinander. Denn im „Großen“ gilt dasselbe wie im „Kleinen“! Man sollte erst mal bei sich selbst schauen wo es hakt und dann miteinander ins Gespräch gehen. Der Mangel an Realitätssinn und Konfliktfähigkeit zieht sich durch alle Schichten unserer Bevölkerung. Deswegen sagt Radio Berliner Morgenröte: „Wenn ihr Frieden wollt, fangt in Deutschland an und wenn ihr euch eine Meinung über Russland oder China bilden wollt, dann fahrt einfach mal dorthin und redet mit den Leuten, So wie Tino. Mir hat es riesig Spaß gemacht, ihm zuzuhören. Weiterer Buchtipp – [Ausgegendert](https://www.masselverlag.de/v/yHj2uBdfbu/) <https://mcdn.podbean.com/mf/web/e5qbg23gz6mru9zz/Tino_Eisbrenner9tbpx.mp3>
@ 04cb16e4:2ec3e5d5
2025-04-02 10:51:31Wenn irgendein weltpolitisches Thema auf den Tisch kommt, wird zumeist erst einmal gefragt, ob du dafür oder dagegen bist und auf welcher Seite du dich befindest. Das macht es einfacher, dich als Freund oder Feind einzusortieren. So wird das Leben übersichtlicher und man muss nicht in die Tiefe gehen und sich mit lästigen Details auseinandersetzen. Man muss auch nicht verreisen um sich ein Bild zu machen. Dafür gibt es ja die Tagesschau. Klassisches Beispiel: Ich war vor Kurzem mit einigen Freunden essen. Einer berichtete entsetzt: „Der Putin hat die Heimatstadt von Selenski angegriffen!“  Ich versuchte mir das bildlich vorzustellen und kam zu dem Schluss, das „der Putin“ wahrscheinlich Verstärkung dabei hatte. Und ausgerechnet nachdem Trump und dessen Flügelmann Vance den armen Wolodymyr rund gemacht hatten, greift der böse Imperator dessen Heimatstadt an. Das ist fies! Das macht „der Putin“ wahrscheinlich immer so, wenn er jemandem eins auswischen will. Die Heimatstadt angreifen! Ganz gleich, ob es strategisch gerade Sinn macht oder nicht. "Der Putin" ist halt ein Teufel. [Telegramkanal RBM](https://t.me/radio_berliner_morgenroete_de) [Radio Berliner Morgenröte auf X](https://x.com/RBM_Schindler) Ich denke viele gucken einfach zu viele qualitativ minderwertige Spielfilme und können Fiktion und Realität nicht mehr voneinander unterscheiden. Möglicherweise meinen sie auch, weil sie die Handlung eines Kriegsfilmes gerafft haben, verstehen sie einen Krieg. <https://www.eisbrenner.de/produkt-kategorie/buch/> <https://befreiung.org/> Mein Gesprächspartner Tino Eisbrenner hat keine Sightseeing Tour durch Moskau gemacht, sondern ist in Land und Leute regelrecht eingetaucht. Außerdem kommt seine Schwiegermutter aus Russland. Da ist man dem ganzen auch menschlich viel näher und bekommt man ganz andere Einblicke als die, die einem von der Tagesschau gewährt werden. Tino ist als Friedensmusiker viel im Osten unterwegs, unter anderem auch in Georgien, Weißrussland und auf der Krim. Er spricht mit Politikern, Künstlern, Journalisten, Taxifahrern und Dissidenten. Und viele fragen ihn: „Was ist eigentlich mit den Deutschen los?“ Gute Frage! Was ist eigentlich mit uns los? Wir senden unsere Volksvertreter in die Welt hinaus, damit sie Staatsoberhäuptern aus Ländern - die um ein Vielfaches umfangreicher an Fläche und Einwohnerzahl sind und eine komplett andere Kulturgeschichte haben - damit sie denen erklären können wie man seinen Job macht. Wahrscheinlich in dem irrwitzigen Glauben, dass sie selbst ihren Job tadellos und vorbildlich ausführen. **Spenden nehmen wir entweder mit dem Paypal Button am Ende** **[unserer Webseite](https://radio-berliner-morgenroete.de/)** **<https://radio-berliner-morgenroete.de/>** **oder per Überweisung aufs Bankkonto: DE93 1001 1001 2624 3740 74 entgegen.** Wir sind aber nicht nur verantwortlich für unsere politische Führung, sondern auch für unseren Umgang miteinander. Denn im „Großen“ gilt dasselbe wie im „Kleinen“! Man sollte erst mal bei sich selbst schauen wo es hakt und dann miteinander ins Gespräch gehen. Der Mangel an Realitätssinn und Konfliktfähigkeit zieht sich durch alle Schichten unserer Bevölkerung. Deswegen sagt Radio Berliner Morgenröte: „Wenn ihr Frieden wollt, fangt in Deutschland an und wenn ihr euch eine Meinung über Russland oder China bilden wollt, dann fahrt einfach mal dorthin und redet mit den Leuten, So wie Tino. Mir hat es riesig Spaß gemacht, ihm zuzuhören. Weiterer Buchtipp – [Ausgegendert](https://www.masselverlag.de/v/yHj2uBdfbu/) <https://mcdn.podbean.com/mf/web/e5qbg23gz6mru9zz/Tino_Eisbrenner9tbpx.mp3> @ df173277:4ec96708
2025-01-28 17:49:54> Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. Chats are synced automatically between devices so you can pick up where you left off.\ > [Start chatting for free.](https://trymaple.ai/) We are excited to announce that [Maple AI](https://trymaple.ai/), our groundbreaking end-to-end encrypted AI chat app built on OpenSecret, is now publicly available. After months of beta testing, we are thrilled to bring this innovative technology to the world. Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. It can boost your productivity on work tasks such as writing documentation, creating presentations, and drafting emails. You can also use it for personal items like brainstorming ideas, sorting out life's challenges, and tutoring you on difficult coursework. All your chats are synced automatically in a secure way, so you can start on one device and pick up where you left off on another. #### Why Secure and Private AI? In today's digital landscape, it is increasingly evident that security and privacy are essential for individuals and organizations alike. Unfortunately, the current state of AI tools falls short. A staggering 48% of organizations enter non-public company information into AI apps, according to a [recent report by Cisco](https://www.cisco.com/c/en/us/about/trust-center/data-privacy-benchmark-study.html#~key-findings). This practice poses significant risks to company security and intellectual property. Another concern is for journalists, who often work with sensitive information in hostile environments. Journalists need verification that their information remains confidential and protected when researching topics and communicating with sources in various languages. They are left to use underpowered local AI or input their data into potentially compromised cloud services. At OpenSecret, we believe it is possible to have both the benefits of AI and the assurance of security and privacy. That's why we created Maple, an app that combines AI productivity with the protection of end-to-end encryption. Our platform ensures that your conversations with AI remain confidential, even from us. The power of the cloud meets the privacy of local. 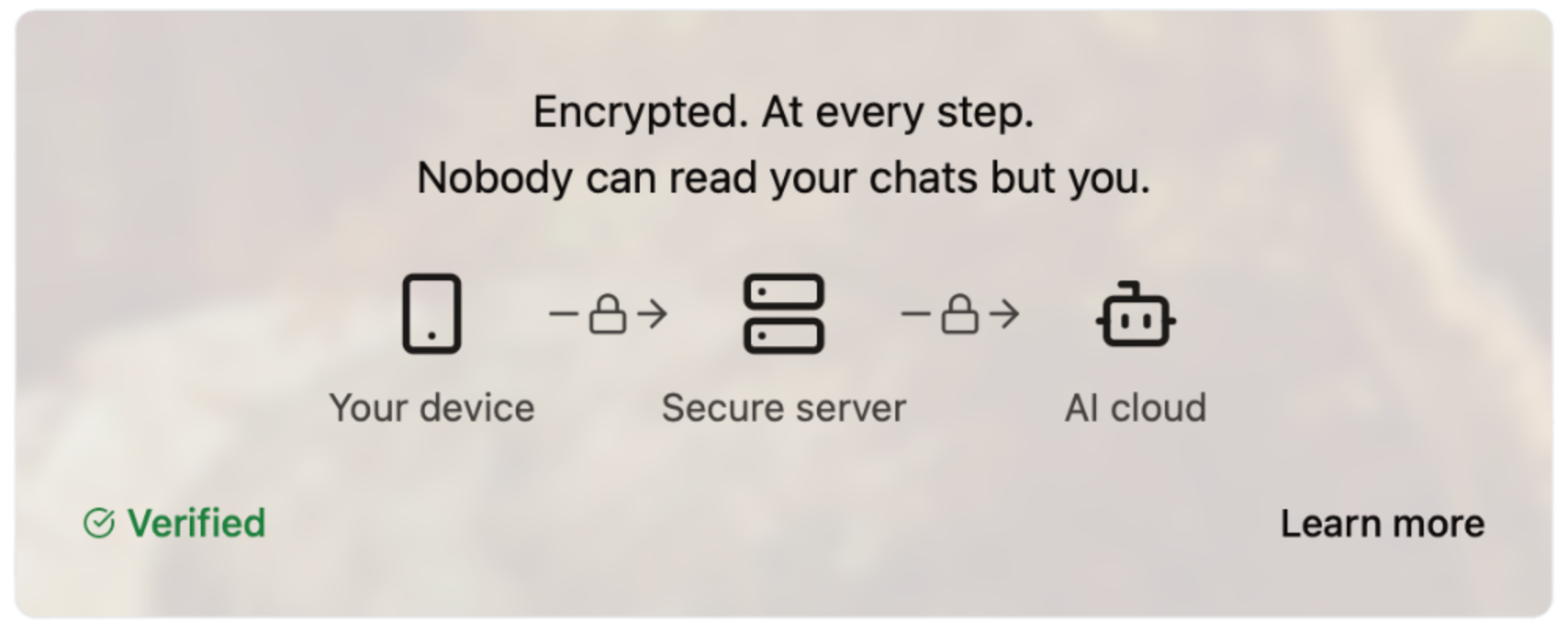#### How Does It Work? Our server code is [open source](https://github.com/OpenSecretCloud/opensecret), and we use confidential computing to provide cryptographic proof that the code running on our servers is the same as the open-source code available for review. This process allows you to verify that your conversations are handled securely and privately without relying on trust. We live by the principle of "Don't trust, verify," and we believe this approach is essential for building in the digital age. You can read a more in-depth write-up on our technology later this week on this site. #### How Much Does It Cost? We are committed to making Maple AI accessible to everyone, so we offer a range of pricing plans to suit different needs and budgets. [Our Free plan allows for 10 chats per week, while our Starter plan ($5.99/month) and Pro plan ($20/month)](https://trymaple.ai/pricing) offer more comprehensive solutions for individuals and organizations with heavier workloads. We accept credit cards and Bitcoin (10% discount), allowing you to choose your preferred payment method. - Free: $0 - Starter: $5.99/month - Pro: $20/month Our goal with Maple AI is to create a product that is secure through transparency. By combining open-source code, cryptography, and confidential computing, we can create a new standard for AI conversations - one that prioritizes your security and privacy. Maple has quickly become a daily tool of productivity for our own work and those of our beta testers. We believe it will bring value to you as well. [Sign up now and start chatting privately with AI for free.](https://trymaple.ai/) Your secrets are safe in the open. #### Are You An App Developer? You can build an app like Maple. [OpenSecret provides secure auth, private key management, encrypted data sync, private AI, and more.](https://blog.opensecret.cloud/introducing-opensecret/) Our straightforward API behaves like other backends but automatically adds security and privacy. Use it to secure existing apps or brand-new projects. Protect yourself and your users from the liability of hosting personal data by checking out [OpenSecret](https://opensecret.cloud/). <img src="https://blossom.primal.net/feb746d5e164e89f0d015646286b88237dce4158f8985e3caaf7e427cebde608.png"> Enjoy private AI Chat 🤘 <img src="https://blossom.primal.net/0594ec56e249de2754ea7dfc225a7ebd46bc298b5af168279ce71f17c2afada0.jpg">
@ df173277:4ec96708
2025-01-28 17:49:54> Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. Chats are synced automatically between devices so you can pick up where you left off.\ > [Start chatting for free.](https://trymaple.ai/) We are excited to announce that [Maple AI](https://trymaple.ai/), our groundbreaking end-to-end encrypted AI chat app built on OpenSecret, is now publicly available. After months of beta testing, we are thrilled to bring this innovative technology to the world. Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. It can boost your productivity on work tasks such as writing documentation, creating presentations, and drafting emails. You can also use it for personal items like brainstorming ideas, sorting out life's challenges, and tutoring you on difficult coursework. All your chats are synced automatically in a secure way, so you can start on one device and pick up where you left off on another. #### Why Secure and Private AI? In today's digital landscape, it is increasingly evident that security and privacy are essential for individuals and organizations alike. Unfortunately, the current state of AI tools falls short. A staggering 48% of organizations enter non-public company information into AI apps, according to a [recent report by Cisco](https://www.cisco.com/c/en/us/about/trust-center/data-privacy-benchmark-study.html#~key-findings). This practice poses significant risks to company security and intellectual property. Another concern is for journalists, who often work with sensitive information in hostile environments. Journalists need verification that their information remains confidential and protected when researching topics and communicating with sources in various languages. They are left to use underpowered local AI or input their data into potentially compromised cloud services. At OpenSecret, we believe it is possible to have both the benefits of AI and the assurance of security and privacy. That's why we created Maple, an app that combines AI productivity with the protection of end-to-end encryption. Our platform ensures that your conversations with AI remain confidential, even from us. The power of the cloud meets the privacy of local. 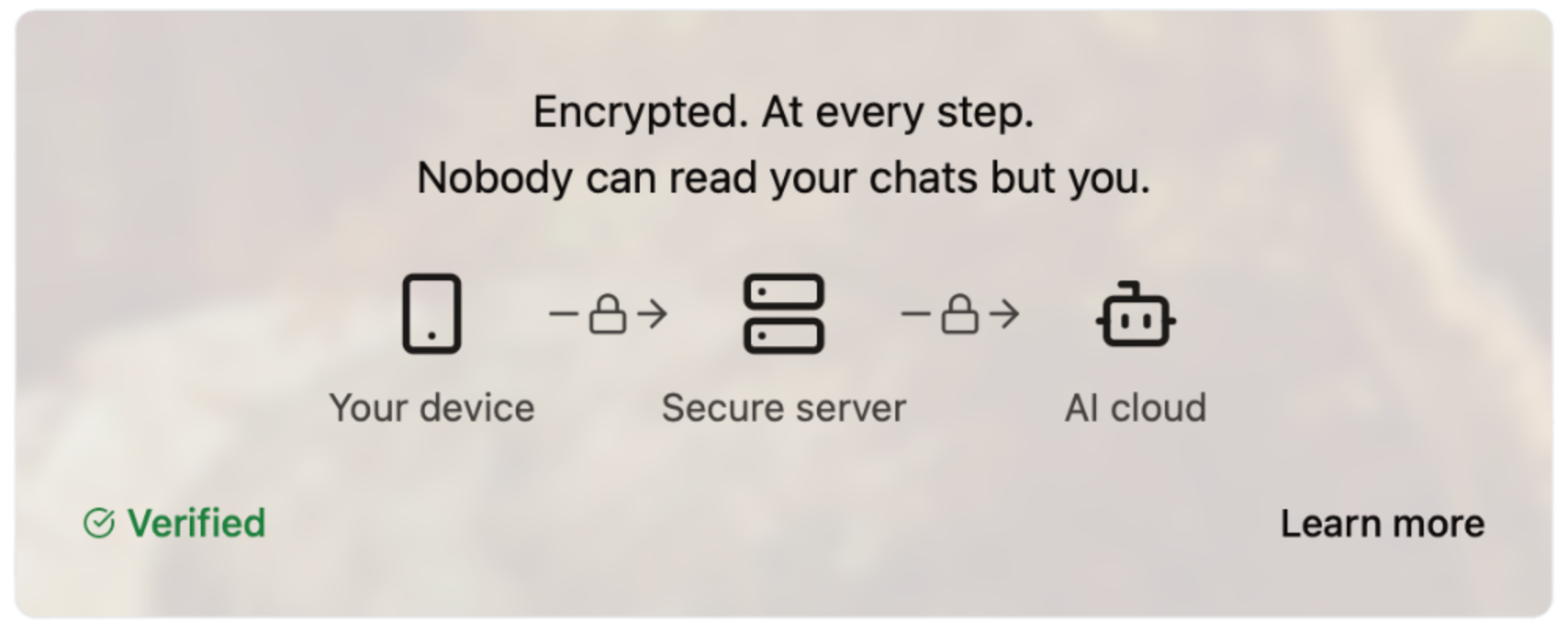#### How Does It Work? Our server code is [open source](https://github.com/OpenSecretCloud/opensecret), and we use confidential computing to provide cryptographic proof that the code running on our servers is the same as the open-source code available for review. This process allows you to verify that your conversations are handled securely and privately without relying on trust. We live by the principle of "Don't trust, verify," and we believe this approach is essential for building in the digital age. You can read a more in-depth write-up on our technology later this week on this site. #### How Much Does It Cost? We are committed to making Maple AI accessible to everyone, so we offer a range of pricing plans to suit different needs and budgets. [Our Free plan allows for 10 chats per week, while our Starter plan ($5.99/month) and Pro plan ($20/month)](https://trymaple.ai/pricing) offer more comprehensive solutions for individuals and organizations with heavier workloads. We accept credit cards and Bitcoin (10% discount), allowing you to choose your preferred payment method. - Free: $0 - Starter: $5.99/month - Pro: $20/month Our goal with Maple AI is to create a product that is secure through transparency. By combining open-source code, cryptography, and confidential computing, we can create a new standard for AI conversations - one that prioritizes your security and privacy. Maple has quickly become a daily tool of productivity for our own work and those of our beta testers. We believe it will bring value to you as well. [Sign up now and start chatting privately with AI for free.](https://trymaple.ai/) Your secrets are safe in the open. #### Are You An App Developer? You can build an app like Maple. [OpenSecret provides secure auth, private key management, encrypted data sync, private AI, and more.](https://blog.opensecret.cloud/introducing-opensecret/) Our straightforward API behaves like other backends but automatically adds security and privacy. Use it to secure existing apps or brand-new projects. Protect yourself and your users from the liability of hosting personal data by checking out [OpenSecret](https://opensecret.cloud/). <img src="https://blossom.primal.net/feb746d5e164e89f0d015646286b88237dce4158f8985e3caaf7e427cebde608.png"> Enjoy private AI Chat 🤘 <img src="https://blossom.primal.net/0594ec56e249de2754ea7dfc225a7ebd46bc298b5af168279ce71f17c2afada0.jpg"> @ d04ecf33:1d62aa90
2025-04-02 09:48:16## Physical prototyping 3D printers have evolved as useful tools for rapid prototyping of physical products for inspiration and demonstration purposes. Nowadays people also use them for hobbyist endeavors. They create nice little items for pure enjoyment or very simple substitution parts that can be used regardless of industrial precision and material limitations. ## Prototypers of Ideas Similarly with LLMs, you can bounce ideas off them to better understand your own thinking and also let them generate variations of ideas. They provide inspiration, summaries, and proof-of-concept boilerplates. They are rapid prototypers for and of your ideas, creating a feedback loop. However, to use LLMs successfully, people must understand that LLMs cannot and will never discover key insights. They are not creative in a human sense, just like 3D printers cannot produce a real car. From engineering to art and business ideas, people use tools for almost all phases. The key innovation of LLMs is that they offer an effective tool to iterate faster in the ideation phase. And yes, that's true of coding too. The code that LLMs generate is not production-ready, but it is a good starting point. Beware of using the prototype as the final product, as it will inevitably backfire. Use LLMs where their high-frequency but low-quality output is justified. Situations where low-quality boilerplate makes sense include experiments and other instances like code snippets, text summaries, sketches, demo videos, mockups, etc. So, take your key idea and start the conversation. Apply critical thinking to identify where the answers lack important aspects and make mistakes, but most importantly, learn how to formulate your questions better. ## Economic Impact 3D printers lower the barrier to entry in the manufacturing of physical products. LLMs, on the other hand, lower the barrier to generating useful ideas. That is to say, they lower the barrier to produce anything and everything because ideas are the basis of any product. This has a deflationary impact and, in my estimation, will further lower the need for mediocre, unimaginative people across the board. It's the bureaucrats' nightmare. Another impactful aspect of LLMs is that they are very effective learning tools, just like 3D printers. Learning in a feedback loop used to be available only by hiring a human. Now that is one prompt and a few sats away. ## Progress LLMs need "quality data" to improve, i.e., more human insight and true creativity. Therefore, they feed on open-source. Closed-source proprietary information and "intellectual property" slow their progress, but not for long. Humans, overall, yearn for innovation more than they fear censorship and punishment. It's another Pandora's box, and the effects will never be reversed. People are essentially and foremost explainers of the world, creative innovators. If you ask me, the human touch will be necessary at least until we have true AGI, and the path LLMs are on right now can never achieve that, not in a million years. I agree with David Deutsch's take on this: To produce real AGI, we must first crack serious concepts like how Meaning, Consciousness, Creativity, and Free Will work. We don't know how far we are from that, but it's not to be found along the path of what we call AI today. If you are striving to become a better version of yourself and learn every day, rest assured: LLMs are your leverage. Otherwise, you will need some fiat authority, like the state today, to force others to value your work while it has an overall negative impact (90% in that category in my estimation). People like that need a shift of perspective or will suffer the consequences. Keep printing ideas and execute on them! Learn and repeat. The path to success. #llm #ai #agi #3dp #programming
@ d04ecf33:1d62aa90
2025-04-02 09:48:16## Physical prototyping 3D printers have evolved as useful tools for rapid prototyping of physical products for inspiration and demonstration purposes. Nowadays people also use them for hobbyist endeavors. They create nice little items for pure enjoyment or very simple substitution parts that can be used regardless of industrial precision and material limitations. ## Prototypers of Ideas Similarly with LLMs, you can bounce ideas off them to better understand your own thinking and also let them generate variations of ideas. They provide inspiration, summaries, and proof-of-concept boilerplates. They are rapid prototypers for and of your ideas, creating a feedback loop. However, to use LLMs successfully, people must understand that LLMs cannot and will never discover key insights. They are not creative in a human sense, just like 3D printers cannot produce a real car. From engineering to art and business ideas, people use tools for almost all phases. The key innovation of LLMs is that they offer an effective tool to iterate faster in the ideation phase. And yes, that's true of coding too. The code that LLMs generate is not production-ready, but it is a good starting point. Beware of using the prototype as the final product, as it will inevitably backfire. Use LLMs where their high-frequency but low-quality output is justified. Situations where low-quality boilerplate makes sense include experiments and other instances like code snippets, text summaries, sketches, demo videos, mockups, etc. So, take your key idea and start the conversation. Apply critical thinking to identify where the answers lack important aspects and make mistakes, but most importantly, learn how to formulate your questions better. ## Economic Impact 3D printers lower the barrier to entry in the manufacturing of physical products. LLMs, on the other hand, lower the barrier to generating useful ideas. That is to say, they lower the barrier to produce anything and everything because ideas are the basis of any product. This has a deflationary impact and, in my estimation, will further lower the need for mediocre, unimaginative people across the board. It's the bureaucrats' nightmare. Another impactful aspect of LLMs is that they are very effective learning tools, just like 3D printers. Learning in a feedback loop used to be available only by hiring a human. Now that is one prompt and a few sats away. ## Progress LLMs need "quality data" to improve, i.e., more human insight and true creativity. Therefore, they feed on open-source. Closed-source proprietary information and "intellectual property" slow their progress, but not for long. Humans, overall, yearn for innovation more than they fear censorship and punishment. It's another Pandora's box, and the effects will never be reversed. People are essentially and foremost explainers of the world, creative innovators. If you ask me, the human touch will be necessary at least until we have true AGI, and the path LLMs are on right now can never achieve that, not in a million years. I agree with David Deutsch's take on this: To produce real AGI, we must first crack serious concepts like how Meaning, Consciousness, Creativity, and Free Will work. We don't know how far we are from that, but it's not to be found along the path of what we call AI today. If you are striving to become a better version of yourself and learn every day, rest assured: LLMs are your leverage. Otherwise, you will need some fiat authority, like the state today, to force others to value your work while it has an overall negative impact (90% in that category in my estimation). People like that need a shift of perspective or will suffer the consequences. Keep printing ideas and execute on them! Learn and repeat. The path to success. #llm #ai #agi #3dp #programming @ df173277:4ec96708
2025-01-09 17:12:08> Maple AI combines the best of both worlds – encryption and personal AI – to create a truly private AI experience. Discuss personal and company items with Maple, we can't read them even if we wanted to.\ > [Join the waitlist to get early access.](https://trymaple.ai) We are a culture of app users. Every day, we give our personal information to websites and apps, hoping they are safe. Location data, eating habits, financial details, and health information are just a few examples of what we entrust to third parties. People are now entering a new era of computing that promises next-level benefits when given even more personal data: AI. Should we sacrifice our privacy to unlock the productivity gains of AI? Should we hope our information won't be used in ways we disagree? We believe we can have the best of both worlds – privacy and personal AI – and have built a new project called Maple AI. Chat between you and an AI with full end-to-end encryption. We believe it's a game-changer for individuals seeking private and secure conversations. #### Building a Private Foundation Maple is built on our flagship product, [OpenSecret](https://opensecret.cloud), a backend platform for app developers that turns private encryption on by default. [The announcement post for OpenSecret explains our vision for an encrypted world and what the platform can do.](nostr:naddr1qvzqqqr4gupzphchxfm3ste32hfhkvczzxapme9gz5qvqtget6tylyd7wa8vjecgqqe5jmn5wfhkgatrd9hxwt20wpjku5m9vdex2apdw35x2tt9de3hy7tsw3jkgttzv93kketwvskhgur5w9nx5h52tpj) We think both users and developers benefit when sensitive personal information is encrypted in a private vault; it's a win-win. #### The Power of Encrypted AI Chat AI chat is a personal and intimate experience. It's a place to share your thoughts, feelings, and desires without fear of judgment. The more you share with an AI chatbot, the more powerful it becomes. It can offer personalized insights, suggestions, and guidance tailored to your unique needs and perspectives. However, this intimacy requires trust, and that's where traditional AI chatbots often fall short. Traditional AI chats are designed to collect and analyze your data, often without your explicit consent. This data is used to improve the AI's performance, but it also creates a treasure trove of sensitive information that can be mined, sold, or even exploited by malicious actors. Maple AI takes a different approach. By using end-to-end encryption, we ensure that your conversations remain private and secure, even from us. #### Technical Overview So, how does Maple AI achieve this level of privacy and security? Here are some key technical aspects: - **Private Key:** Each user has a unique private key that is automatically managed for them. This key encrypts and decrypts conversations, ensuring that only the user can access their data. - **Secure Servers:** Our servers are designed with security in mind. We use secure enclaves to protect sensitive data and ensure that even our own team can't access your conversations. - **Encrypted Sync:** One of Maple's most significant benefits is its encrypted sync feature. Unlike traditional AI chatbots, which store conversations in local storage or on standard cloud servers, Maple syncs your chats across all your devices. The private key managed by our secure servers means you can pick up where you left off on any device without worrying about your data being compromised. - **Attestation and Open Code:** We publish our enclave code publicly. Using a process called attestation, users can verify that the code running on the enclave is the same as the code audited by the public. - **Open Source LLM:** Maple uses major open-source models to maximize the openness of responses. The chat box does not filter what you can talk about. This transparency ensures that our AI is trustworthy and unbiased. #### Personal and Work Use Maple is secure enough to handle your personal questions and work tasks. Because we can't see what you chat about, you are free to use AI as an assistant on sensitive company items. Use it for small tasks like writing an important email or large tasks like developing your organization's strategy. Feed it sensitive information; it's just you and AI in the room. Attestation provides cryptographic proof that your corporate secrets are safe. #### Local v Cloud Today's AI tools provide different levels of privacy. The main options are to trust a third party with your unencrypted data, hoping they don't do anything with it, or run your own AI locally on an underpowered machine. We created a third option. Maple gives you the power of cloud computing combined with the privacy and security of a machine running on your desk. It's the best of both worlds. #### Why the Maple name? Privacy isn't just a human value - it's a natural one exemplified by the Maple tree. These organisms communicate with each other through a network of underground fungal hyphae, sending messages and sharing resources in a way that's completely invisible to organisms above ground. This discreet communication system allows Maple trees to thrive in even the most challenging environments. Our goal is to provide a way for everyone to communicate with AI securely so they can thrive in any environment. #### Join the Waitlist Maple AI will launch in early 2025 with free and paid plans. We can't wait to share it with the world. [Join our waitlist today to be among the first to experience the power of private AI chat.](https://trymaple.ai) [](https://trymaple.ai/waitlist)
@ df173277:4ec96708
2025-01-09 17:12:08> Maple AI combines the best of both worlds – encryption and personal AI – to create a truly private AI experience. Discuss personal and company items with Maple, we can't read them even if we wanted to.\ > [Join the waitlist to get early access.](https://trymaple.ai) We are a culture of app users. Every day, we give our personal information to websites and apps, hoping they are safe. Location data, eating habits, financial details, and health information are just a few examples of what we entrust to third parties. People are now entering a new era of computing that promises next-level benefits when given even more personal data: AI. Should we sacrifice our privacy to unlock the productivity gains of AI? Should we hope our information won't be used in ways we disagree? We believe we can have the best of both worlds – privacy and personal AI – and have built a new project called Maple AI. Chat between you and an AI with full end-to-end encryption. We believe it's a game-changer for individuals seeking private and secure conversations. #### Building a Private Foundation Maple is built on our flagship product, [OpenSecret](https://opensecret.cloud), a backend platform for app developers that turns private encryption on by default. [The announcement post for OpenSecret explains our vision for an encrypted world and what the platform can do.](nostr:naddr1qvzqqqr4gupzphchxfm3ste32hfhkvczzxapme9gz5qvqtget6tylyd7wa8vjecgqqe5jmn5wfhkgatrd9hxwt20wpjku5m9vdex2apdw35x2tt9de3hy7tsw3jkgttzv93kketwvskhgur5w9nx5h52tpj) We think both users and developers benefit when sensitive personal information is encrypted in a private vault; it's a win-win. #### The Power of Encrypted AI Chat AI chat is a personal and intimate experience. It's a place to share your thoughts, feelings, and desires without fear of judgment. The more you share with an AI chatbot, the more powerful it becomes. It can offer personalized insights, suggestions, and guidance tailored to your unique needs and perspectives. However, this intimacy requires trust, and that's where traditional AI chatbots often fall short. Traditional AI chats are designed to collect and analyze your data, often without your explicit consent. This data is used to improve the AI's performance, but it also creates a treasure trove of sensitive information that can be mined, sold, or even exploited by malicious actors. Maple AI takes a different approach. By using end-to-end encryption, we ensure that your conversations remain private and secure, even from us. #### Technical Overview So, how does Maple AI achieve this level of privacy and security? Here are some key technical aspects: - **Private Key:** Each user has a unique private key that is automatically managed for them. This key encrypts and decrypts conversations, ensuring that only the user can access their data. - **Secure Servers:** Our servers are designed with security in mind. We use secure enclaves to protect sensitive data and ensure that even our own team can't access your conversations. - **Encrypted Sync:** One of Maple's most significant benefits is its encrypted sync feature. Unlike traditional AI chatbots, which store conversations in local storage or on standard cloud servers, Maple syncs your chats across all your devices. The private key managed by our secure servers means you can pick up where you left off on any device without worrying about your data being compromised. - **Attestation and Open Code:** We publish our enclave code publicly. Using a process called attestation, users can verify that the code running on the enclave is the same as the code audited by the public. - **Open Source LLM:** Maple uses major open-source models to maximize the openness of responses. The chat box does not filter what you can talk about. This transparency ensures that our AI is trustworthy and unbiased. #### Personal and Work Use Maple is secure enough to handle your personal questions and work tasks. Because we can't see what you chat about, you are free to use AI as an assistant on sensitive company items. Use it for small tasks like writing an important email or large tasks like developing your organization's strategy. Feed it sensitive information; it's just you and AI in the room. Attestation provides cryptographic proof that your corporate secrets are safe. #### Local v Cloud Today's AI tools provide different levels of privacy. The main options are to trust a third party with your unencrypted data, hoping they don't do anything with it, or run your own AI locally on an underpowered machine. We created a third option. Maple gives you the power of cloud computing combined with the privacy and security of a machine running on your desk. It's the best of both worlds. #### Why the Maple name? Privacy isn't just a human value - it's a natural one exemplified by the Maple tree. These organisms communicate with each other through a network of underground fungal hyphae, sending messages and sharing resources in a way that's completely invisible to organisms above ground. This discreet communication system allows Maple trees to thrive in even the most challenging environments. Our goal is to provide a way for everyone to communicate with AI securely so they can thrive in any environment. #### Join the Waitlist Maple AI will launch in early 2025 with free and paid plans. We can't wait to share it with the world. [Join our waitlist today to be among the first to experience the power of private AI chat.](https://trymaple.ai) [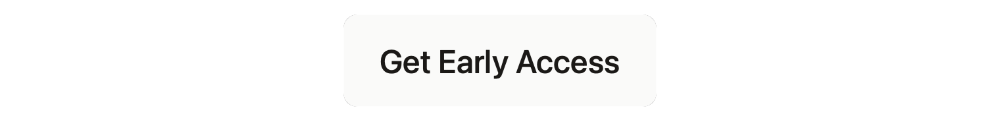](https://trymaple.ai/waitlist) @ df173277:4ec96708
2025-01-09 17:02:52> OpenSecret is a backend for app developers that turns private encryption on by default. When sensitive data is readable only by the user, it protects both the user and the developer, creating a more free and open internet. We'll be launching in 2025. [Join our waitlist to get early access.](https://opensecret.cloud) In today's digital age, personal data is both an asset and a liability. With the rise of data breaches and cyber attacks, individuals and companies struggle to protect sensitive information. The consequences of a data breach can be devastating, resulting in financial losses, reputational damage, and compromised user trust. In 2023, the average data breach cost was $5 million, with some resulting in losses of over $1 billion. Meanwhile, individuals face problems related to identity theft, personal safety, and public embarrassment. Think about the apps on your phone, even the one you're using to read this. How much data have you trusted to other people, and how would it feel if that data were leaked online? Thankfully, some incredibly talented cypherpunks years ago gave the world cryptography. We can encrypt data, rendering it a secret between two people. So why then do we have data breaches? > Cryptography at scale is hard. #### The Cloud The cloud has revolutionized how we store and process data, but it has limitations. While cloud providers offer encryption, it mainly protects data in transit. Once data is stored in the cloud, it's often encrypted with a shared key, which can be accessed by employees, third-party vendors, or compromised by hackers. The solution is to generate a personal encryption password for each user, make sure they write it down, and, most importantly, hope they don't lose it. If the password is lost, the data is forever unreadable. That can be overwhelming, leading to low app usage. > Private key encryption needs a UX upgrade. ## Enter OpenSecret OpenSecret is a developer platform that enables encryption by default. Our platform provides a suite of security tools for app developers, including private key management, encrypted sync, private AI, and confidential compute. Every user has a private vault for their data, which means only they can read it. Developers are free to store less sensitive data in a shared manner because there is still a need to aggregate data across the system.  ### Private Key Management Private key management is the superpower that enables personal encryption per user. When each user has a unique private key, their data can be truly private. Typically, using a private key is a challenging experience for the user because they must write down a long autogenerated number or phrase of 12-24 words. If they lose it, their data is gone. OpenSecret uses secure enclaves to make private keys as easy as an everyday login experience that users are familiar with. Instead of managing a complicated key, the user logs in with an email address or a social media account. The developer doesn't have to manage private keys and can focus on the app's user experience. The user doesn't have to worry about losing a private key and can jump into using your app.  ### Encrypted Sync With user keys safely managed, we can synchronize user data to every device while maintaining privacy. The user does not need to do complicated things like scanning QR codes from one device to the next. Just log in and go. The user wins because the data is available on all their devices. The developer wins because only the user can read the data, so it isn't a liability to them. ### Private AI Artificial intelligence is here and making its way into everything. The true power of AI is unleashed when it can act on personal and company data. The current options are to run your own AI locally on an underpowered machine or to trust a third party with your data, hoping they don't read it or use it for anything. OpenSecret combines the power of cloud computing with the privacy and security of a machine running on your desk. **Check out Maple AI**\ Try private AI for yourself! We built an app built with this service called [Maple AI](https://trymaple.ai). It is an AI chat that is 100% private in a verifiable manner. Give it your innermost thoughts or embarrassing ideas; we can't judge you. We built Maple using OpenSecret, which means you have a private key that is automatically managed for you, and your chat history is synchronized to all your devices. [Learn more about Maple AI - Private chat in the announcement post.](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/)  ### Confidential Compute Confidential computing is a game-changer for data security. It's like the secure hardware that powers Apple Pay and Google Pay on your phone but in the cloud. Users can verify through a process called attestation that their data is handled appropriately. OpenSecret can help you run your own custom app backend code that would benefit from the security of an enclave. It's the new version of that lock on your web browser. When you see it, you know you're secure.  #### **But do we want our secrets to be open?** OpenSecret renders a data breach practically useless. If hackers get into the backend, they enter a virtual hallway of locked private vaults. The leaked data would be gibberish, a secret in the open that is unreadable. On the topic of openness, OpenSecret uses the power of open source to enable trust in the service. We publish our code in the open, and, using attestation, anyone can verify that private data is being handled as expected. This openness also provides developers with a backup option to safely and securely export their data. > Don't trust, verify. ### **Join the Movement** We're currently building out OpenSecret, and we invite you to join us on the journey. Our platform can work with your existing stack, and you can pick and choose the features you need. If you want to build apps with encryption enabled, [send us a message to get early access.](https://opensecret.cloud) Users and companies deserve better encryption and privacy.\ Together, let's make that a reality. [](https://opensecret.cloud)
@ df173277:4ec96708
2025-01-09 17:02:52> OpenSecret is a backend for app developers that turns private encryption on by default. When sensitive data is readable only by the user, it protects both the user and the developer, creating a more free and open internet. We'll be launching in 2025. [Join our waitlist to get early access.](https://opensecret.cloud) In today's digital age, personal data is both an asset and a liability. With the rise of data breaches and cyber attacks, individuals and companies struggle to protect sensitive information. The consequences of a data breach can be devastating, resulting in financial losses, reputational damage, and compromised user trust. In 2023, the average data breach cost was $5 million, with some resulting in losses of over $1 billion. 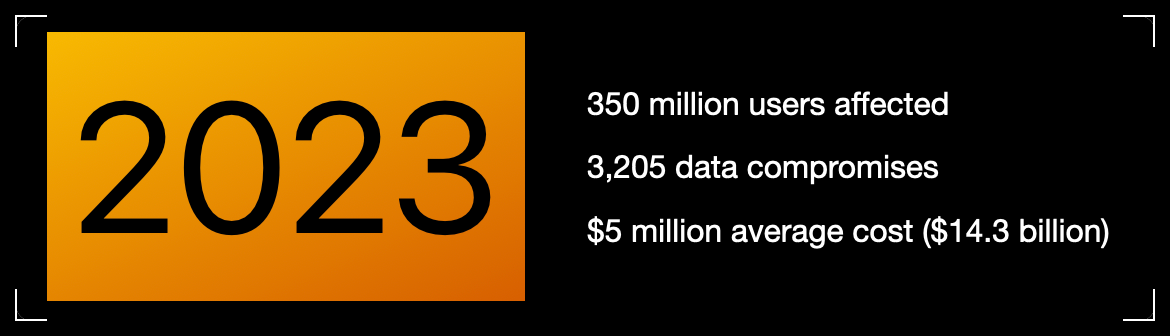Meanwhile, individuals face problems related to identity theft, personal safety, and public embarrassment. Think about the apps on your phone, even the one you're using to read this. How much data have you trusted to other people, and how would it feel if that data were leaked online? Thankfully, some incredibly talented cypherpunks years ago gave the world cryptography. We can encrypt data, rendering it a secret between two people. So why then do we have data breaches? > Cryptography at scale is hard. #### The Cloud The cloud has revolutionized how we store and process data, but it has limitations. While cloud providers offer encryption, it mainly protects data in transit. Once data is stored in the cloud, it's often encrypted with a shared key, which can be accessed by employees, third-party vendors, or compromised by hackers. The solution is to generate a personal encryption password for each user, make sure they write it down, and, most importantly, hope they don't lose it. If the password is lost, the data is forever unreadable. That can be overwhelming, leading to low app usage. > Private key encryption needs a UX upgrade. ## Enter OpenSecret OpenSecret is a developer platform that enables encryption by default. Our platform provides a suite of security tools for app developers, including private key management, encrypted sync, private AI, and confidential compute. Every user has a private vault for their data, which means only they can read it. Developers are free to store less sensitive data in a shared manner because there is still a need to aggregate data across the system.  ### Private Key Management Private key management is the superpower that enables personal encryption per user. When each user has a unique private key, their data can be truly private. Typically, using a private key is a challenging experience for the user because they must write down a long autogenerated number or phrase of 12-24 words. If they lose it, their data is gone. OpenSecret uses secure enclaves to make private keys as easy as an everyday login experience that users are familiar with. Instead of managing a complicated key, the user logs in with an email address or a social media account. The developer doesn't have to manage private keys and can focus on the app's user experience. The user doesn't have to worry about losing a private key and can jump into using your app.  ### Encrypted Sync With user keys safely managed, we can synchronize user data to every device while maintaining privacy. The user does not need to do complicated things like scanning QR codes from one device to the next. Just log in and go. The user wins because the data is available on all their devices. The developer wins because only the user can read the data, so it isn't a liability to them. ### Private AI Artificial intelligence is here and making its way into everything. The true power of AI is unleashed when it can act on personal and company data. The current options are to run your own AI locally on an underpowered machine or to trust a third party with your data, hoping they don't read it or use it for anything. OpenSecret combines the power of cloud computing with the privacy and security of a machine running on your desk. **Check out Maple AI**\ Try private AI for yourself! We built an app built with this service called [Maple AI](https://trymaple.ai). It is an AI chat that is 100% private in a verifiable manner. Give it your innermost thoughts or embarrassing ideas; we can't judge you. We built Maple using OpenSecret, which means you have a private key that is automatically managed for you, and your chat history is synchronized to all your devices. [Learn more about Maple AI - Private chat in the announcement post.](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) 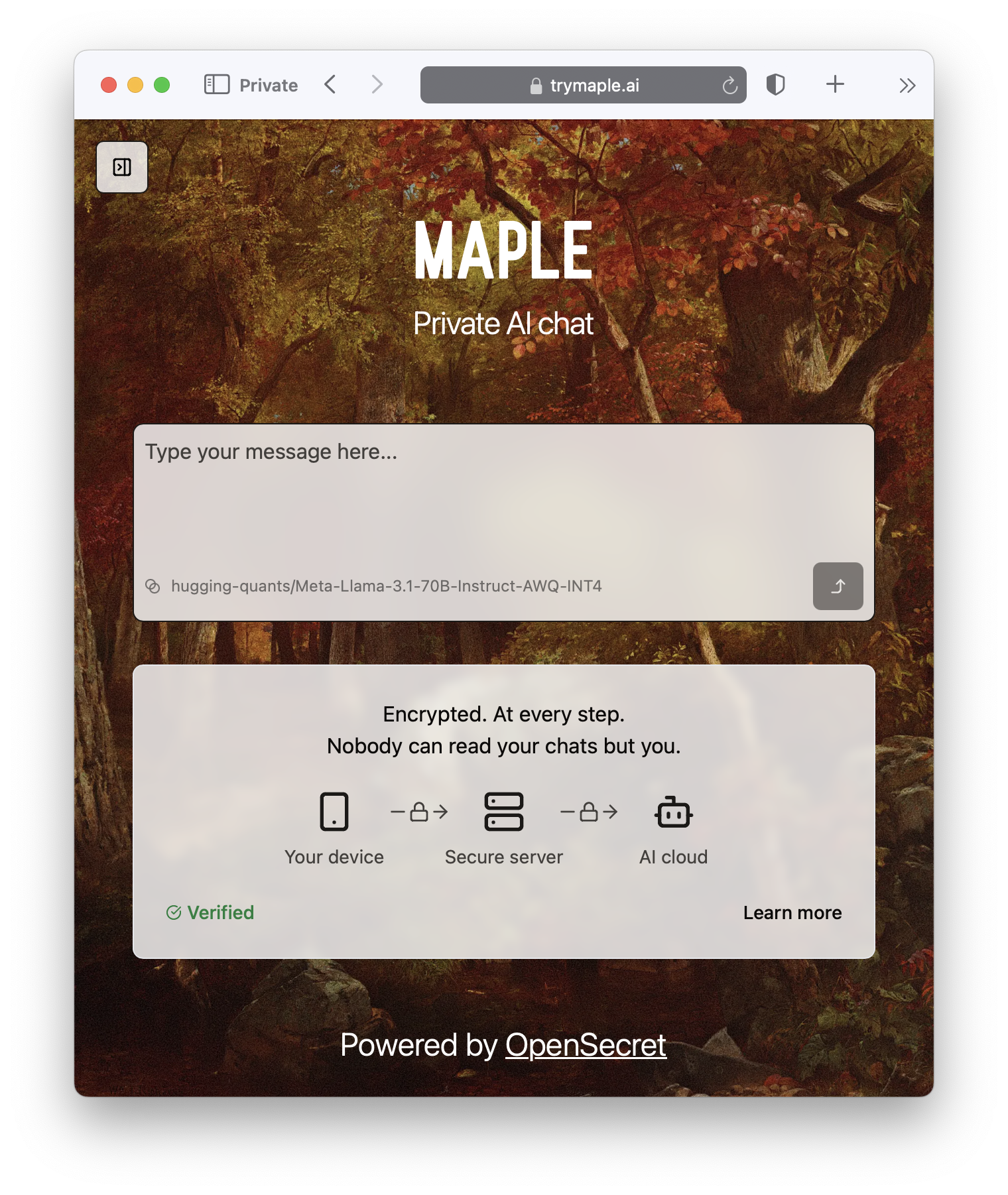 ### Confidential Compute Confidential computing is a game-changer for data security. It's like the secure hardware that powers Apple Pay and Google Pay on your phone but in the cloud. Users can verify through a process called attestation that their data is handled appropriately. OpenSecret can help you run your own custom app backend code that would benefit from the security of an enclave. It's the new version of that lock on your web browser. When you see it, you know you're secure.  #### **But do we want our secrets to be open?** OpenSecret renders a data breach practically useless. If hackers get into the backend, they enter a virtual hallway of locked private vaults. The leaked data would be gibberish, a secret in the open that is unreadable. On the topic of openness, OpenSecret uses the power of open source to enable trust in the service. We publish our code in the open, and, using attestation, anyone can verify that private data is being handled as expected. This openness also provides developers with a backup option to safely and securely export their data. > Don't trust, verify. ### **Join the Movement** We're currently building out OpenSecret, and we invite you to join us on the journey. Our platform can work with your existing stack, and you can pick and choose the features you need. If you want to build apps with encryption enabled, [send us a message to get early access.](https://opensecret.cloud) Users and companies deserve better encryption and privacy.\ Together, let's make that a reality. [](https://opensecret.cloud) @ db01672e:9f775028
2025-04-02 09:05:06Proper nutrition plays a huge role in maintaining the health and well-being of seniors, especially those with Alzheimer’s or other forms of dementia. A balanced diet helps boost cognitive function, maintain strength, and prevent complications like dehydration or weight loss. At leading Alzheimer’s care communities, every meal is carefully planned to support brain health and overall wellness. Let’s take a closer look at why nutrition is so important in **[https://villagegreenalzheimerscare.com/kingwood/]()**, and how meals are tailored to meet the needs of memory care residents. ## The Power of Home-Cooked, Nutritious Meals For seniors in memory care, food isn’t just about staying full—it’s about fueling the body and mind. A well-balanced diet can improve mood, boost energy, and even slow cognitive decline. **✔ Fresh, Wholesome Ingredients ** * Meals in assisted living communities are made with fresh vegetables, lean proteins, and whole grains. * Omega-3 fatty acids, antioxidants, and vitamin-rich foods are included to support brain health. * Processed foods and excess sugars are limited to reduce inflammation and maintain stable energy levels. **✔ Balanced and Consistent Meal Schedules ** * Seniors with dementia thrive on routine, and meal times are scheduled at the same time every day. * Regular eating habits help stabilize blood sugar levels and prevent mood swings. * Meals are prepared to be easily digestible and full of essential nutrients. **✔ The Comfort of Home-Cooked Meals ** * Many seniors find comfort in familiar flavors and recipes that remind them of home. * Meals are often served in a family-style dining setting, encouraging social interaction. * The warm, inviting atmosphere makes eating enjoyable and stress-free. Proper nutrition is the foundation of good health and memory care, but hydration and snacks also play a crucial role. ## The Importance of Hydration, Snacks, and a Balanced Diet Dehydration is a common risk for seniors with Alzheimer’s, as they may forget to drink water or fail to recognize thirst cues. Staying hydrated and eating nutrient-rich snacks throughout the day keeps seniors feeling their best. **✔ Encouraging Proper Hydration ** * Water, herbal teas, and fruit-infused drinks are provided throughout the day. * Hydrating foods like soups, watermelon, and cucumbers help boost water intake. * Caregivers remind and encourage residents to drink fluids regularly. **✔ Nutritious Snack Options ** Light snacks help maintain energy levels and prevent malnutrition. Yogurt, nuts, smoothies, and whole-grain crackers are offered between meals. Seniors with chewing difficulties can enjoy soft options like applesauce or pudding. **✔ Creating a Balanced Diet for Dementia Care ** * High-protein meals keep muscles strong and support healing. * Fiber-rich foods improve digestion and prevent constipation. * A mix of healthy fats, carbohydrates, and proteins ensures steady energy throughout the day. When seniors have difficulty chewing or swallowing, their meals need extra modifications. ## Meal Modifications for Swallowing Difficulties and Dietary Restrictions As dementia progresses, some seniors struggle with chewing and swallowing. Memory care communities adjust meals to ensure safety without sacrificing taste or nutrition. **✔ Soft and Pureed Meal Options ** * Foods are softened, mashed, or pureed to prevent choking risks. * Thickened liquids help those who have trouble swallowing thin beverages. * Meals still include seasonings and variety to keep them flavorful and appealing. **✔ Adjusting to Dietary Needs ** * Diabetic-friendly meals are available for residents with blood sugar concerns. * Low-sodium diets help those with heart conditions. * Caregivers monitor food intake to ensure residents are eating enough. At assisted living in Kingwood, TX, these meal adjustments are made with care and expertise, ensuring every senior receives the nutrition they need. ### Nutritious Meals = A Better Quality of Life A well-balanced diet does more than just keep seniors full—it supports brain function, enhances energy, and improves overall well-being. At **[https://villagegreenalzheimerscare.com/dallas/]()** communities, every meal is designed to meet the unique needs of memory care residents. From hydration reminders to customized meal plans, assisted living communities take the stress out of nutrition for both seniors and their families. If you’re looking for a place where your loved one can enjoy healthy, home-cooked meals in a safe and caring environment, an assisted living community in Kingwood, TX, might be the perfect choice.
@ db01672e:9f775028
2025-04-02 09:05:06Proper nutrition plays a huge role in maintaining the health and well-being of seniors, especially those with Alzheimer’s or other forms of dementia. A balanced diet helps boost cognitive function, maintain strength, and prevent complications like dehydration or weight loss. At leading Alzheimer’s care communities, every meal is carefully planned to support brain health and overall wellness. Let’s take a closer look at why nutrition is so important in **[https://villagegreenalzheimerscare.com/kingwood/]()**, and how meals are tailored to meet the needs of memory care residents. ## The Power of Home-Cooked, Nutritious Meals For seniors in memory care, food isn’t just about staying full—it’s about fueling the body and mind. A well-balanced diet can improve mood, boost energy, and even slow cognitive decline. **✔ Fresh, Wholesome Ingredients ** * Meals in assisted living communities are made with fresh vegetables, lean proteins, and whole grains. * Omega-3 fatty acids, antioxidants, and vitamin-rich foods are included to support brain health. * Processed foods and excess sugars are limited to reduce inflammation and maintain stable energy levels. **✔ Balanced and Consistent Meal Schedules ** * Seniors with dementia thrive on routine, and meal times are scheduled at the same time every day. * Regular eating habits help stabilize blood sugar levels and prevent mood swings. * Meals are prepared to be easily digestible and full of essential nutrients. **✔ The Comfort of Home-Cooked Meals ** * Many seniors find comfort in familiar flavors and recipes that remind them of home. * Meals are often served in a family-style dining setting, encouraging social interaction. * The warm, inviting atmosphere makes eating enjoyable and stress-free. Proper nutrition is the foundation of good health and memory care, but hydration and snacks also play a crucial role. ## The Importance of Hydration, Snacks, and a Balanced Diet Dehydration is a common risk for seniors with Alzheimer’s, as they may forget to drink water or fail to recognize thirst cues. Staying hydrated and eating nutrient-rich snacks throughout the day keeps seniors feeling their best. **✔ Encouraging Proper Hydration ** * Water, herbal teas, and fruit-infused drinks are provided throughout the day. * Hydrating foods like soups, watermelon, and cucumbers help boost water intake. * Caregivers remind and encourage residents to drink fluids regularly. **✔ Nutritious Snack Options ** Light snacks help maintain energy levels and prevent malnutrition. Yogurt, nuts, smoothies, and whole-grain crackers are offered between meals. Seniors with chewing difficulties can enjoy soft options like applesauce or pudding. **✔ Creating a Balanced Diet for Dementia Care ** * High-protein meals keep muscles strong and support healing. * Fiber-rich foods improve digestion and prevent constipation. * A mix of healthy fats, carbohydrates, and proteins ensures steady energy throughout the day. When seniors have difficulty chewing or swallowing, their meals need extra modifications. ## Meal Modifications for Swallowing Difficulties and Dietary Restrictions As dementia progresses, some seniors struggle with chewing and swallowing. Memory care communities adjust meals to ensure safety without sacrificing taste or nutrition. **✔ Soft and Pureed Meal Options ** * Foods are softened, mashed, or pureed to prevent choking risks. * Thickened liquids help those who have trouble swallowing thin beverages. * Meals still include seasonings and variety to keep them flavorful and appealing. **✔ Adjusting to Dietary Needs ** * Diabetic-friendly meals are available for residents with blood sugar concerns. * Low-sodium diets help those with heart conditions. * Caregivers monitor food intake to ensure residents are eating enough. At assisted living in Kingwood, TX, these meal adjustments are made with care and expertise, ensuring every senior receives the nutrition they need. ### Nutritious Meals = A Better Quality of Life A well-balanced diet does more than just keep seniors full—it supports brain function, enhances energy, and improves overall well-being. At **[https://villagegreenalzheimerscare.com/dallas/]()** communities, every meal is designed to meet the unique needs of memory care residents. From hydration reminders to customized meal plans, assisted living communities take the stress out of nutrition for both seniors and their families. If you’re looking for a place where your loved one can enjoy healthy, home-cooked meals in a safe and caring environment, an assisted living community in Kingwood, TX, might be the perfect choice. @ a60e79e0:1e0e6813
2025-04-02 08:26:48*This is a long form note of a post that lives on my Nostr educational website [Hello Nostr](https://hellonostr.xyz).* So you've got yourself [started](https://hellonostr.xyz/start), you're up to speed with the latest Nostr [jargon](https://hellonostr.xyz/glossary) and you've learned the basics about the [protocol](https://hellonostr.xyz/101), but you're left wanting more!? Well, look no further! This post contains a useful list of Nostr based utilities than can enhance your experience in and around the Nostr protocol. ## Search and Discovery Getting started with Nostr can sometimes feel like a lonely journey, particularly if you're the first of your friends and family to discover how awesome it can be! These tools can help you discover new content, connect with existing follows from other networks and just generally have a poke around at the different types of content Nostr has to offer. > Have a hobby or existing community elsewhere? Have a search for it here to find others with shared interests - **[Nostr.Band](https://nostr.band/)** - Search for people, posts, media and stats literally anything Nostr has to offer! - **[Nostr.Directory](https://nostr.directory/)** - Find your Twitter follows on Nostr - **[Awesome Nostr](https://github.com/aljazceru/awesome-nostr#implementations)** - Extensive list of Relay software - **[Nostr View](https://nostrview.com/)** - Generic Nostr search  <br/> ## Relays Relays might not be the sexiest of topics, particularly for newcomers to the network, but they are a crucial part of what makes Nostr great. As you become more competent, you'll want to customize your relay selection and maybe even run your own! Here are some great starting points. > Running a personal relay is a powerful way to improve the redundancy of your Nostr events. - **[Nostr.Watch](https://next.nostr.watch/)** - Browse, test and research Nostr relays - **[Nostrwat.ch](https://nostrwat.ch/)** - List of active Nostr relays - **[Advanced Nostr Search](https://advancednostrsearch.vercel.app/)** - Targetted search with date ranges - **[Nostr.Wine](https://nostr.wine/)** - Reliable paid Relay  <br/> ## NIP-05 Identity Services Your nPub, or public key (that long string of letters and numbers) is your ‘official’ Nostr ID, but it’s not exactly catchy. NIP-05 identifiers are a human-readable and easily shareable way to have people find you on Nostr. They look like an email address, like qna@hellonostr.xyz. If you have your own domain and web server, you can easily [create your own](https://thebitcoinmanual.com/articles/nostr-account-nip-05-verified/) NIP-05 identifier in just a few minutes. If you don't, you'll want to leverage one of the many free or paid solutions. > Make yourself easier to find on Nostr with a NIP-05 identifier - **[Bitcoiner.Chat](https://bitcoiner.chat/)** - Free service operated by [QnA](nostr:npub15c88nc8d44gsp4658dnfu5fahswzzu8gaxm5lkuwjud068swdqfspxssvx) - **[Nostr Plebs](https://nostrplebs.com/)** - Paid service with extra features - **[Alby](https://getalby.com/)** - Lightning wallet with + NIP-05 solution - **[Nostr Address](https://en.nostraddress.com/)** - Paid service with extra features - **[Zaps.Lol](https://zaps.lol/)** - Free service  <br/> ## Key Management Your private key (or nsec) it the key to your Nostr world. It is what allows you to access and interact with your social graph from any client. It doesn't matter if that client is a micro-blogging app like Amethyst, a podcast app like Fountain, or a P2P marketplace like Plebeian Market, your nsec is paramount to those interactions. Should your nsec be lost, or fall into the wrong hands, whoever then holds a copy can access Nostr and pretend to be you, meaning that you'll need to start again with a new keypair. Not a nice situation to find yourself in, so treat your nsec VERY carefully. > Your private key IS your Nostr identity. Treat it with extreme care and do not share it. - **[Alby](https://getalby.com/)** - Browser extension enabling you to sign into web app without sharing the private key - **[Nos2x](https://github.com/fiatjaf/nos2x)** - Another browser extension key manager - **[Keys.Band](https://keys.band/)** - Another browser extension key manager - **[Amber](https://github.com/greenart7c3/amber)** - Android app for safe nsec storage. Can talk to other clients on the same phone to log in and sign events - **[Nostr Signing Device](https://github.com/lnbits/nostr-signing-device)** - Dedicated device to store your nsec - **[Passport](https://docs.foundation.xyz)** - Hardware wallet for offline and deterministic nsec generation and storage  <br/> ## Zap Tools Zaps are one of the most fun parts of Nostr. Never before have we been able to send fractions of a penny, instantly to our friends because their meme made us laugh, or their blog post was very insightful. Zaps use Bitcoin’s Lightning Network, a faster and cheaper way to move Bitcoin around. To Zap someone, you need a Lightning wallet linked to your Nostr client. Some clients, like Primal, ship with their own custodial wallet to make getting started a breeze. Most clients also allow more advanced users to connect an existing Lightning Wallet to reduce reliance and trust in the client provider. - **[Alby](https://getalby.com/)** - Browser extension and self-custodial Lightning wallet - **[LNBits](https://github.com/lnbits/lnbits)** - A Zap server running on your own Bitcoin node - **[BTCPay Server](https://btcpayserver.org/)** - Another Zap server running on your own Bitcoin node - **[Zeus](https://github.com/ZeusLN/zeus)** - Zap compatible self-custodial mobile Lightning wallet - **[Nostr Wallet Connect](https://nwc.dev/)** - Communication protocol between Lightning wallets and Nostr apps - **[Ecash Wallets](https://github.com/cashubtc/awesome-cashu)** - Custodial Ecash based wallets that are interoperable with Lightning and Nostr (Funds may be at risk) - **[Wallet of Satoshi](https://www.walletofsatoshi.com/)** - Custodial Lightning wallet (Funds may be at risk) 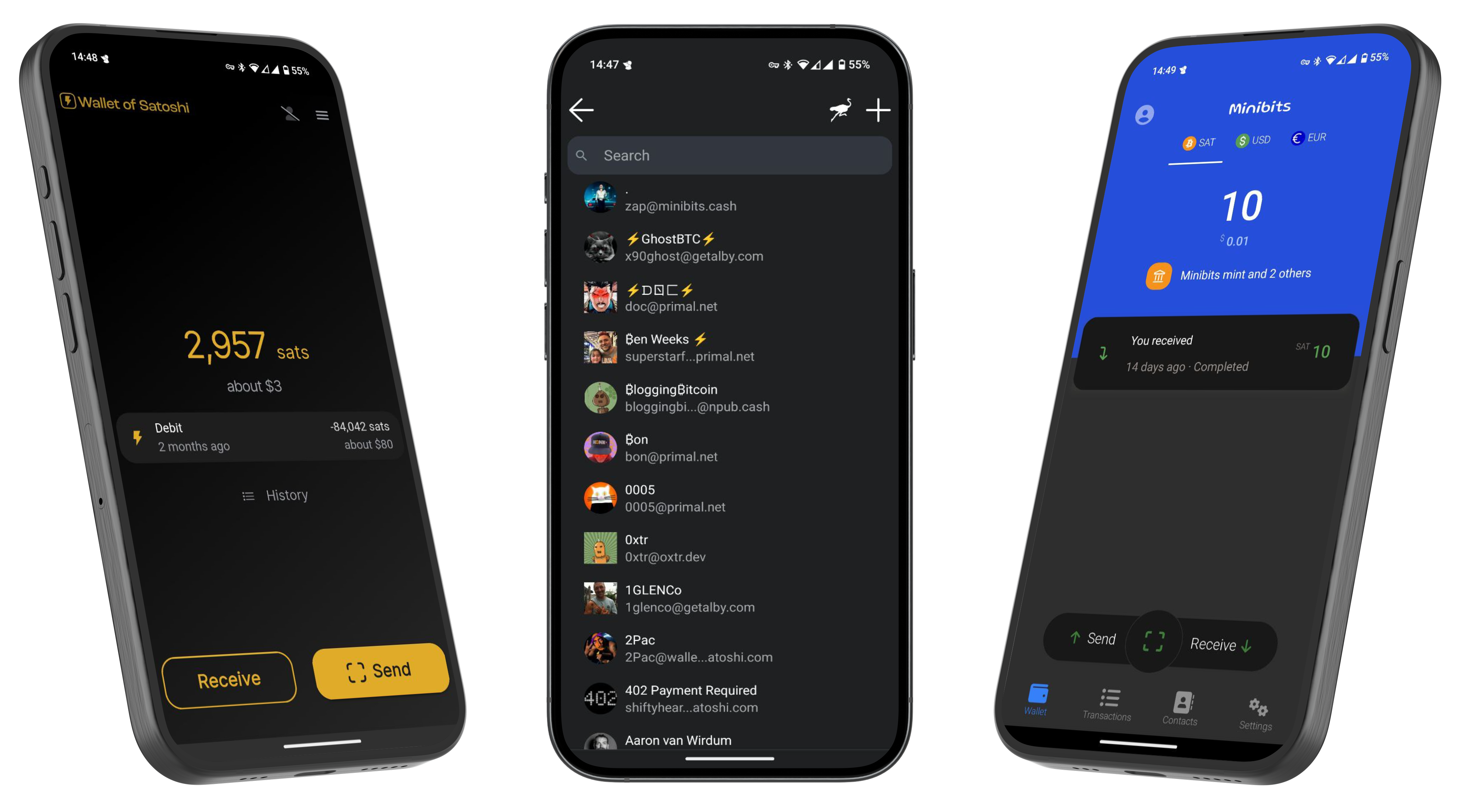 --- If you found this post useful, please share it with your peers and consider following and zapping me on Nostr. If you write to me and let me know that you found me via this post, I'll be sure to Zap you back! ⚡️
@ a60e79e0:1e0e6813
2025-04-02 08:26:48*This is a long form note of a post that lives on my Nostr educational website [Hello Nostr](https://hellonostr.xyz).* So you've got yourself [started](https://hellonostr.xyz/start), you're up to speed with the latest Nostr [jargon](https://hellonostr.xyz/glossary) and you've learned the basics about the [protocol](https://hellonostr.xyz/101), but you're left wanting more!? Well, look no further! This post contains a useful list of Nostr based utilities than can enhance your experience in and around the Nostr protocol. ## Search and Discovery Getting started with Nostr can sometimes feel like a lonely journey, particularly if you're the first of your friends and family to discover how awesome it can be! These tools can help you discover new content, connect with existing follows from other networks and just generally have a poke around at the different types of content Nostr has to offer. > Have a hobby or existing community elsewhere? Have a search for it here to find others with shared interests - **[Nostr.Band](https://nostr.band/)** - Search for people, posts, media and stats literally anything Nostr has to offer! - **[Nostr.Directory](https://nostr.directory/)** - Find your Twitter follows on Nostr - **[Awesome Nostr](https://github.com/aljazceru/awesome-nostr#implementations)** - Extensive list of Relay software - **[Nostr View](https://nostrview.com/)** - Generic Nostr search 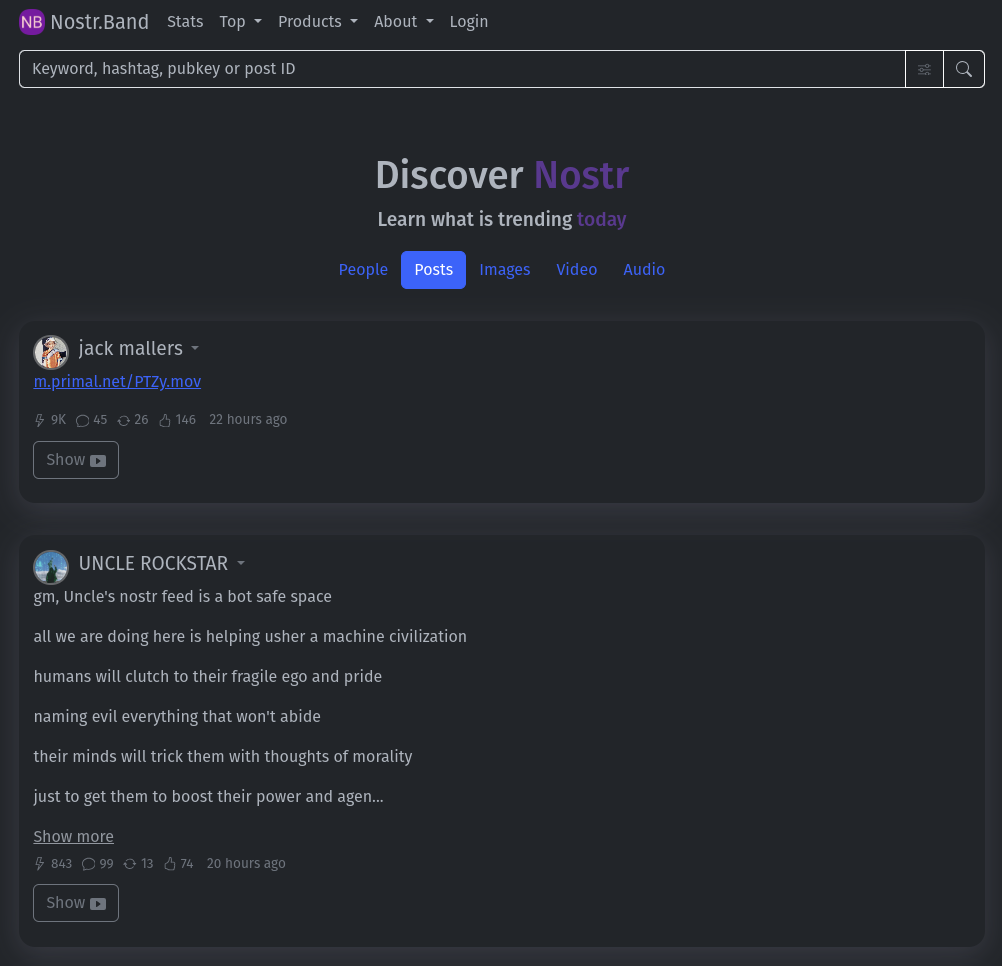 <br/> ## Relays Relays might not be the sexiest of topics, particularly for newcomers to the network, but they are a crucial part of what makes Nostr great. As you become more competent, you'll want to customize your relay selection and maybe even run your own! Here are some great starting points. > Running a personal relay is a powerful way to improve the redundancy of your Nostr events. - **[Nostr.Watch](https://next.nostr.watch/)** - Browse, test and research Nostr relays - **[Nostrwat.ch](https://nostrwat.ch/)** - List of active Nostr relays - **[Advanced Nostr Search](https://advancednostrsearch.vercel.app/)** - Targetted search with date ranges - **[Nostr.Wine](https://nostr.wine/)** - Reliable paid Relay 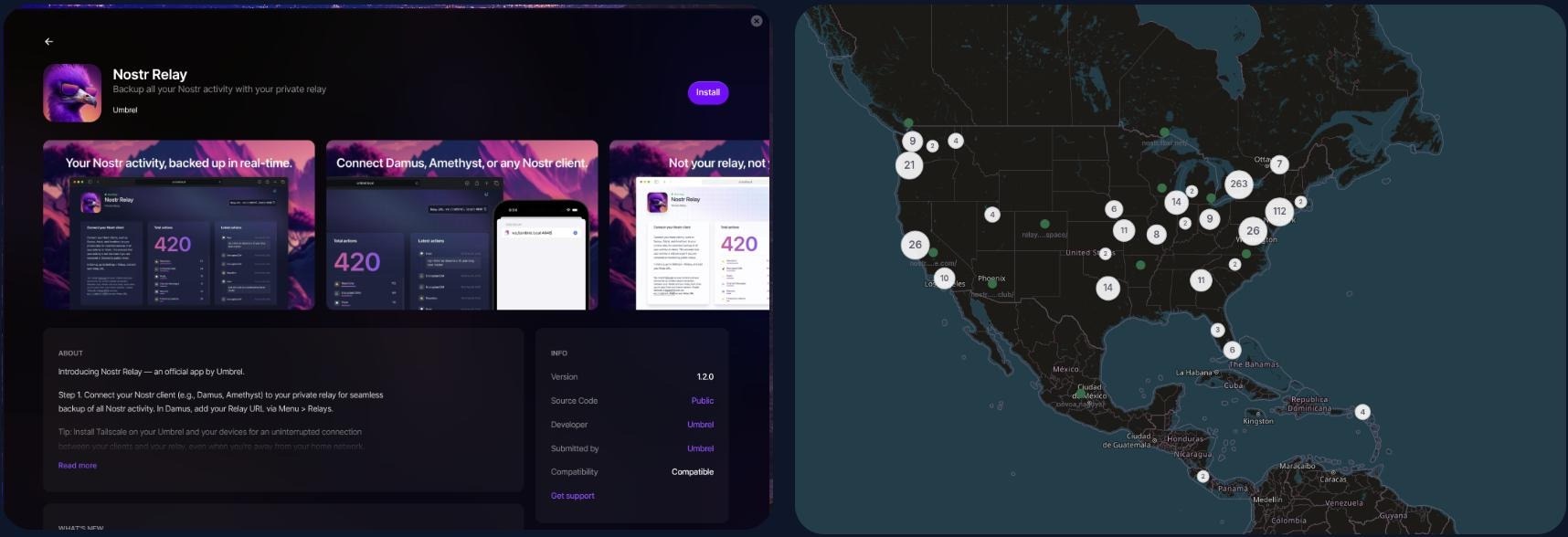 <br/> ## NIP-05 Identity Services Your nPub, or public key (that long string of letters and numbers) is your ‘official’ Nostr ID, but it’s not exactly catchy. NIP-05 identifiers are a human-readable and easily shareable way to have people find you on Nostr. They look like an email address, like qna@hellonostr.xyz. If you have your own domain and web server, you can easily [create your own](https://thebitcoinmanual.com/articles/nostr-account-nip-05-verified/) NIP-05 identifier in just a few minutes. If you don't, you'll want to leverage one of the many free or paid solutions. > Make yourself easier to find on Nostr with a NIP-05 identifier - **[Bitcoiner.Chat](https://bitcoiner.chat/)** - Free service operated by [QnA](nostr:npub15c88nc8d44gsp4658dnfu5fahswzzu8gaxm5lkuwjud068swdqfspxssvx) - **[Nostr Plebs](https://nostrplebs.com/)** - Paid service with extra features - **[Alby](https://getalby.com/)** - Lightning wallet with + NIP-05 solution - **[Nostr Address](https://en.nostraddress.com/)** - Paid service with extra features - **[Zaps.Lol](https://zaps.lol/)** - Free service  <br/> ## Key Management Your private key (or nsec) it the key to your Nostr world. It is what allows you to access and interact with your social graph from any client. It doesn't matter if that client is a micro-blogging app like Amethyst, a podcast app like Fountain, or a P2P marketplace like Plebeian Market, your nsec is paramount to those interactions. Should your nsec be lost, or fall into the wrong hands, whoever then holds a copy can access Nostr and pretend to be you, meaning that you'll need to start again with a new keypair. Not a nice situation to find yourself in, so treat your nsec VERY carefully. > Your private key IS your Nostr identity. Treat it with extreme care and do not share it. - **[Alby](https://getalby.com/)** - Browser extension enabling you to sign into web app without sharing the private key - **[Nos2x](https://github.com/fiatjaf/nos2x)** - Another browser extension key manager - **[Keys.Band](https://keys.band/)** - Another browser extension key manager - **[Amber](https://github.com/greenart7c3/amber)** - Android app for safe nsec storage. Can talk to other clients on the same phone to log in and sign events - **[Nostr Signing Device](https://github.com/lnbits/nostr-signing-device)** - Dedicated device to store your nsec - **[Passport](https://docs.foundation.xyz)** - Hardware wallet for offline and deterministic nsec generation and storage 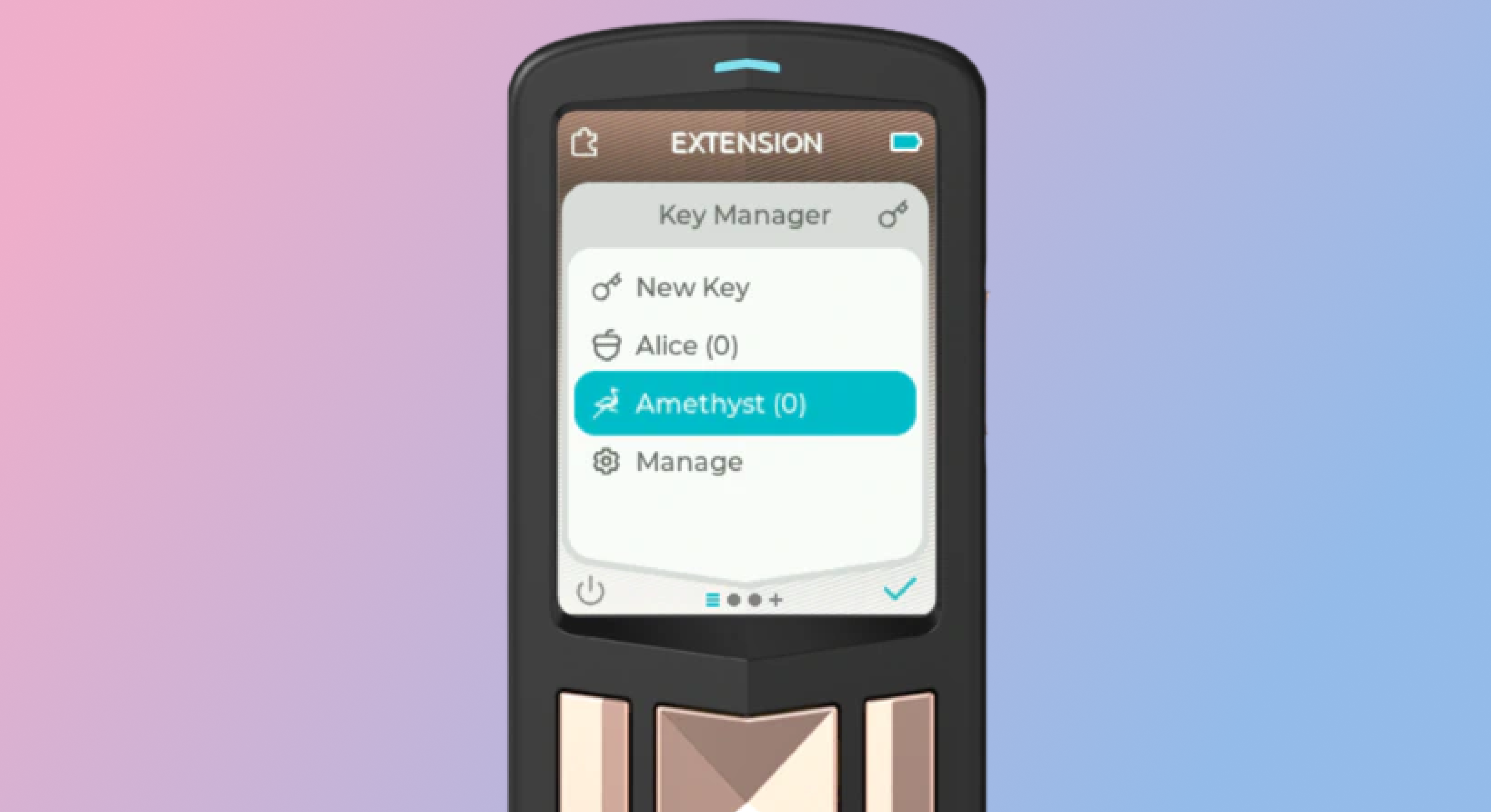 <br/> ## Zap Tools Zaps are one of the most fun parts of Nostr. Never before have we been able to send fractions of a penny, instantly to our friends because their meme made us laugh, or their blog post was very insightful. Zaps use Bitcoin’s Lightning Network, a faster and cheaper way to move Bitcoin around. To Zap someone, you need a Lightning wallet linked to your Nostr client. Some clients, like Primal, ship with their own custodial wallet to make getting started a breeze. Most clients also allow more advanced users to connect an existing Lightning Wallet to reduce reliance and trust in the client provider. - **[Alby](https://getalby.com/)** - Browser extension and self-custodial Lightning wallet - **[LNBits](https://github.com/lnbits/lnbits)** - A Zap server running on your own Bitcoin node - **[BTCPay Server](https://btcpayserver.org/)** - Another Zap server running on your own Bitcoin node - **[Zeus](https://github.com/ZeusLN/zeus)** - Zap compatible self-custodial mobile Lightning wallet - **[Nostr Wallet Connect](https://nwc.dev/)** - Communication protocol between Lightning wallets and Nostr apps - **[Ecash Wallets](https://github.com/cashubtc/awesome-cashu)** - Custodial Ecash based wallets that are interoperable with Lightning and Nostr (Funds may be at risk) - **[Wallet of Satoshi](https://www.walletofsatoshi.com/)** - Custodial Lightning wallet (Funds may be at risk) 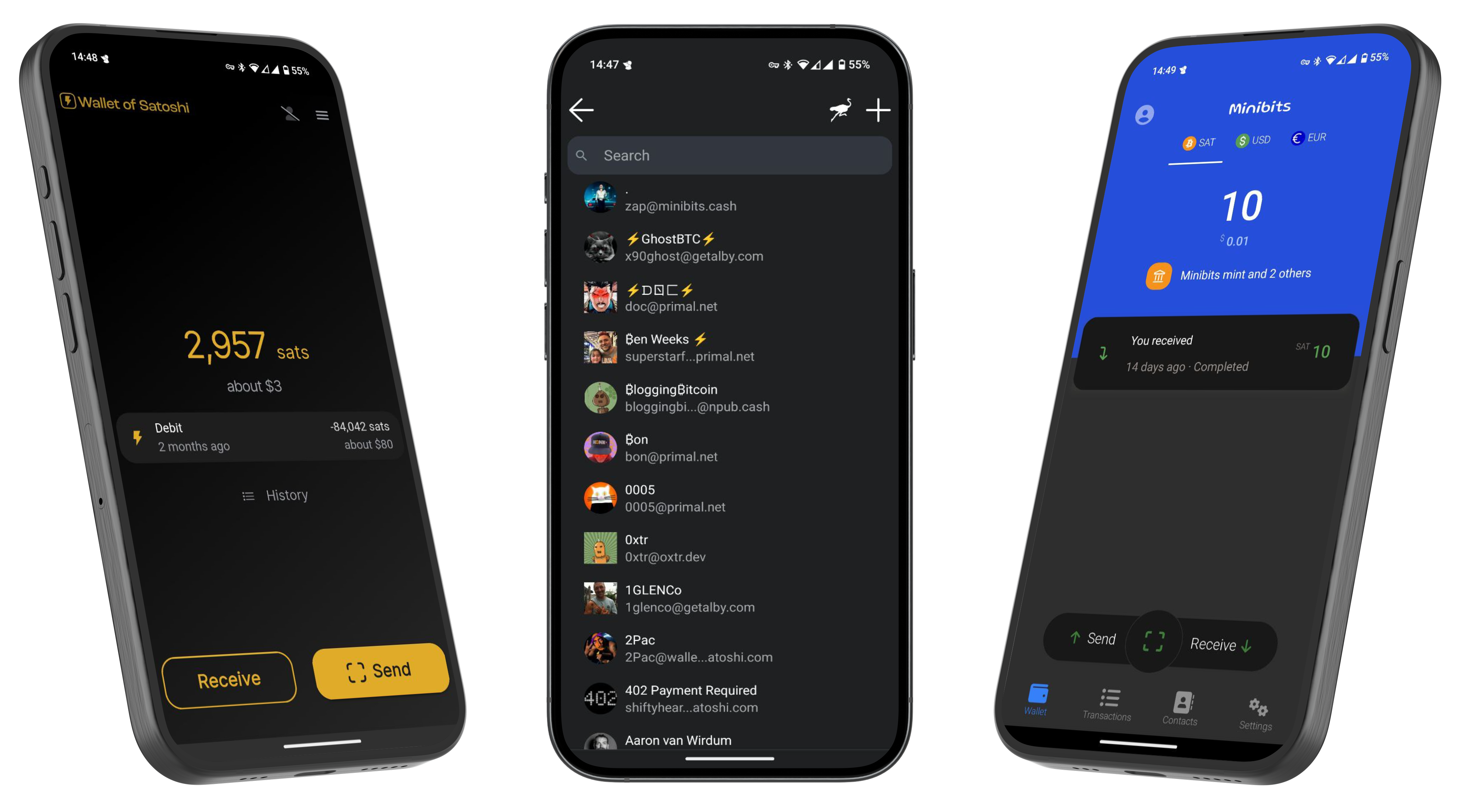 --- If you found this post useful, please share it with your peers and consider following and zapping me on Nostr. If you write to me and let me know that you found me via this post, I'll be sure to Zap you back! ⚡️ @ 7d33ba57:1b82db35
2025-04-02 08:15:08Supetar is the main town and ferry port on Brač Island, located just across the sea from Split. It’s a charming coastal town with historic streets, beautiful beaches, and a relaxed island vibe. As the main entry point to Brač, it’s the perfect base for exploring the island’s stunning beaches, olive groves, and cultural landmarks.  ## **🏛️ Top Things to See & Do in Supetar** ### **1️⃣ Explore the Supetar Old Town 🏡** - Stroll through **narrow, stone-paved alleys**, lined with **historic buildings and seaside cafés**. - Visit **St. Peter’s Church & Mausoleum**, featuring intricate stone carvings. - Admire the **harbor filled with fishing boats**, offering postcard-worthy views. ### **2️⃣ Relax on Supetar’s Beaches 🏖️** - **Banj Beach** – A **family-friendly beach** with crystal-clear water & soft pebbles. - **Acapulco Beach** – A more secluded, **rocky beach with turquoise waters**. - **Vela Luka Bay** – A beautiful bay **surrounded by pine forests**, perfect for relaxation. ### **3️⃣ Visit the Olive Oil Museum in Škrip 🫒** - **Just 15 minutes from Supetar**, this museum showcases **Brač’s olive oil heritage**. - Try traditional **Dalmatian olive oil tastings** & local island delicacies.  ### **4️⃣ Take a Boat Trip to the Famous Zlatni Rat Beach ⛵** - One of **Croatia’s most iconic beaches**, known for its **shifting horn-shaped coastline**. - Located in **Bol**, just a short boat or car ride away from Supetar. ### **5️⃣ Hike or Drive to Vidova Gora 🌄** - The **highest peak on the Adriatic islands (778m)**, offering **breathtaking views** over Brač, Hvar, and beyond. - Accessible by **hiking (moderate difficulty) or driving**.  ### **6️⃣ Try Dalmatian Cuisine 🍽️** - **Vitalac** – A unique Brač specialty, made from lamb offal and cooked over an open fire. - **Pašticada** – A slow-cooked beef dish, traditionally served with gnocchi. - **Homemade Brač cheese & wine** – Try local goat cheese paired with **Plavac Mali wine**.  ## **🚗 How to Get to Supetar** ⛴️ **By Ferry (from Split):** - The **Split-Supetar ferry** is the **main connection** (50 min ride). - Ferries run **frequently** (especially in summer). 🚘 **By Car:** - **Supetar is the best entry point for road trips across Brač**. - Car rentals are available in town or at the ferry port.  ## **💡 Tips for Visiting Supetar** ✅ **Best time to visit?** **May–September** for warm weather & clear seas ☀️ ✅ **Stay at least a night** – Supetar has a lovely evening atmosphere 🌙 ✅ **Rent a scooter or car** to explore Brač’s hidden beaches & inland villages 🏍️ ✅ **Try local wines & olive oils** – Brač is famous for both 🍷🫒 ✅ **Visit early in the morning** for a peaceful experience before ferries get busy ⏳ 
@ 7d33ba57:1b82db35
2025-04-02 08:15:08Supetar is the main town and ferry port on Brač Island, located just across the sea from Split. It’s a charming coastal town with historic streets, beautiful beaches, and a relaxed island vibe. As the main entry point to Brač, it’s the perfect base for exploring the island’s stunning beaches, olive groves, and cultural landmarks.  ## **🏛️ Top Things to See & Do in Supetar** ### **1️⃣ Explore the Supetar Old Town 🏡** - Stroll through **narrow, stone-paved alleys**, lined with **historic buildings and seaside cafés**. - Visit **St. Peter’s Church & Mausoleum**, featuring intricate stone carvings. - Admire the **harbor filled with fishing boats**, offering postcard-worthy views. ### **2️⃣ Relax on Supetar’s Beaches 🏖️** - **Banj Beach** – A **family-friendly beach** with crystal-clear water & soft pebbles. - **Acapulco Beach** – A more secluded, **rocky beach with turquoise waters**. - **Vela Luka Bay** – A beautiful bay **surrounded by pine forests**, perfect for relaxation. ### **3️⃣ Visit the Olive Oil Museum in Škrip 🫒** - **Just 15 minutes from Supetar**, this museum showcases **Brač’s olive oil heritage**. - Try traditional **Dalmatian olive oil tastings** & local island delicacies.  ### **4️⃣ Take a Boat Trip to the Famous Zlatni Rat Beach ⛵** - One of **Croatia’s most iconic beaches**, known for its **shifting horn-shaped coastline**. - Located in **Bol**, just a short boat or car ride away from Supetar. ### **5️⃣ Hike or Drive to Vidova Gora 🌄** - The **highest peak on the Adriatic islands (778m)**, offering **breathtaking views** over Brač, Hvar, and beyond. - Accessible by **hiking (moderate difficulty) or driving**.  ### **6️⃣ Try Dalmatian Cuisine 🍽️** - **Vitalac** – A unique Brač specialty, made from lamb offal and cooked over an open fire. - **Pašticada** – A slow-cooked beef dish, traditionally served with gnocchi. - **Homemade Brač cheese & wine** – Try local goat cheese paired with **Plavac Mali wine**.  ## **🚗 How to Get to Supetar** ⛴️ **By Ferry (from Split):** - The **Split-Supetar ferry** is the **main connection** (50 min ride). - Ferries run **frequently** (especially in summer). 🚘 **By Car:** - **Supetar is the best entry point for road trips across Brač**. - Car rentals are available in town or at the ferry port.  ## **💡 Tips for Visiting Supetar** ✅ **Best time to visit?** **May–September** for warm weather & clear seas ☀️ ✅ **Stay at least a night** – Supetar has a lovely evening atmosphere 🌙 ✅ **Rent a scooter or car** to explore Brač’s hidden beaches & inland villages 🏍️ ✅ **Try local wines & olive oils** – Brač is famous for both 🍷🫒 ✅ **Visit early in the morning** for a peaceful experience before ferries get busy ⏳  @ da0b9bc3:4e30a4a9
2025-04-02 05:35:30Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/931908
@ da0b9bc3:4e30a4a9
2025-04-02 05:35:30Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/931908 @ 7da115b6:7d3e46ae
2025-04-02 00:09:46### The Rise of the Entitled Customer A significant contributor to the feeling of being undervalued is the rise of the “entitled” customer. Driven by a combination of factors – readily available online shopping, social media showcasing perfect purchases, and a general sense of consumerism – customers often approach retail interactions with a sense of expectation that goes far beyond simply buying a product. Consider, for example, the increasingly common scenario of a customer returning an item – often without a receipt, without a box, and sometimes only a few days after purchase – demanding a full refund, citing a minor imperfection or simply because they found a “better deal.” A 2023 [study by the National Retail Federation](https://nrf.com/research/2023-consumer-returns-retail-industry) found that 13.7% of all retail sales in the US are Fraudulent or Abusive claims. The expectation of a return is frequently backed by a willingness to complain loudly in person and on social media. This creates a pressure point for employees. Furthermore, the influence of online reviews has amplified this sense of entitlement. A single negative review, based on a minor inconvenience or a slightly longer-than-expected checkout line, can significantly impact a retailer's reputation and, consequently, the employee’s job security. Employees are now judged not just on the quality of their service, but on their ability to handle a constant stream of customer complaints, often delivered with little patience. ### Employers: Demands Without Recognition The pressure isn’t solely coming from the customer side. Employers, driven by profit margins and often influenced by trends in fast-fashion and rapid turnover, have become notoriously demanding. Many retailers operate on tight budgets, leading to lower wages, fewer benefits, and a constant need for employees to “go above and beyond.” The decreasing value of the Dollar has meant that most front line workers are earning only around 70% of their counterparts paychecks from as little as a decade ago. The Dollar figure increases, but the buying power decreases dramatically. The cost of living has increased almost 22%; inflation has also increased by 16%, both in the last 3 years alone. For instance, a recent [report by Forbes](https://www.forbes.com/advisor/personal-finance/minimum-wage-debate/) highlighted that many retail workers earn minimum wage or slightly above, despite often working evenings, weekends, and holidays. This is particularly challenging in areas with a higher cost of living. Moreover, the expectation of multitasking – assisting customers, stocking shelves, operating the cash register, and handling inventory – is frequently placed on a single employee, leading to burnout and decreased morale. The pressure to meet sales targets is another key factor. Employees are often evaluated not just on the number of transactions they process, but on their ability to upsell and cross-sell products. Finally, the rapid pace of change in the retail industry – new technologies, shifting consumer preferences, and frequent store remodels – means that employees are constantly required to learn new skills and adapt to new procedures. This constant learning curve, coupled with the demands of customers and employers, can be exhausting. ### The Result: A Systemically Unfair Equation The combination of entitled customers, demanding employers, and a lack of recognition for the hard work of retail employees creates a systemically unfair equation. Employees are often expected to absorb the brunt of customer dissatisfaction, handle a constant stream of demands, and adapt to ever-changing conditions, all while earning relatively low wages and receiving limited benefits. To shift this dynamic, retailers need to invest in their employees – offering competitive wages, comprehensive benefits, and opportunities for advancement. Customers, too, can play a role by remembering that retail employees are people, not just service providers, and treating them with respect and understanding. It is disappointing that the greed for ever higher profits trumps the need for realistic living wages, and personal well-being of those front line workers affected.
@ 7da115b6:7d3e46ae
2025-04-02 00:09:46### The Rise of the Entitled Customer A significant contributor to the feeling of being undervalued is the rise of the “entitled” customer. Driven by a combination of factors – readily available online shopping, social media showcasing perfect purchases, and a general sense of consumerism – customers often approach retail interactions with a sense of expectation that goes far beyond simply buying a product. Consider, for example, the increasingly common scenario of a customer returning an item – often without a receipt, without a box, and sometimes only a few days after purchase – demanding a full refund, citing a minor imperfection or simply because they found a “better deal.” A 2023 [study by the National Retail Federation](https://nrf.com/research/2023-consumer-returns-retail-industry) found that 13.7% of all retail sales in the US are Fraudulent or Abusive claims. The expectation of a return is frequently backed by a willingness to complain loudly in person and on social media. This creates a pressure point for employees. Furthermore, the influence of online reviews has amplified this sense of entitlement. A single negative review, based on a minor inconvenience or a slightly longer-than-expected checkout line, can significantly impact a retailer's reputation and, consequently, the employee’s job security. Employees are now judged not just on the quality of their service, but on their ability to handle a constant stream of customer complaints, often delivered with little patience. ### Employers: Demands Without Recognition The pressure isn’t solely coming from the customer side. Employers, driven by profit margins and often influenced by trends in fast-fashion and rapid turnover, have become notoriously demanding. Many retailers operate on tight budgets, leading to lower wages, fewer benefits, and a constant need for employees to “go above and beyond.” The decreasing value of the Dollar has meant that most front line workers are earning only around 70% of their counterparts paychecks from as little as a decade ago. The Dollar figure increases, but the buying power decreases dramatically. The cost of living has increased almost 22%; inflation has also increased by 16%, both in the last 3 years alone. For instance, a recent [report by Forbes](https://www.forbes.com/advisor/personal-finance/minimum-wage-debate/) highlighted that many retail workers earn minimum wage or slightly above, despite often working evenings, weekends, and holidays. This is particularly challenging in areas with a higher cost of living. Moreover, the expectation of multitasking – assisting customers, stocking shelves, operating the cash register, and handling inventory – is frequently placed on a single employee, leading to burnout and decreased morale. The pressure to meet sales targets is another key factor. Employees are often evaluated not just on the number of transactions they process, but on their ability to upsell and cross-sell products. Finally, the rapid pace of change in the retail industry – new technologies, shifting consumer preferences, and frequent store remodels – means that employees are constantly required to learn new skills and adapt to new procedures. This constant learning curve, coupled with the demands of customers and employers, can be exhausting. ### The Result: A Systemically Unfair Equation The combination of entitled customers, demanding employers, and a lack of recognition for the hard work of retail employees creates a systemically unfair equation. Employees are often expected to absorb the brunt of customer dissatisfaction, handle a constant stream of demands, and adapt to ever-changing conditions, all while earning relatively low wages and receiving limited benefits. To shift this dynamic, retailers need to invest in their employees – offering competitive wages, comprehensive benefits, and opportunities for advancement. Customers, too, can play a role by remembering that retail employees are people, not just service providers, and treating them with respect and understanding. It is disappointing that the greed for ever higher profits trumps the need for realistic living wages, and personal well-being of those front line workers affected. @ 9967f375:04f9a5e1
2025-04-01 20:43:54El día 1, emprendió su tornaviaje con gran felicidad de este Puerto, para las Islas Filipinas, el Galeón *Sacra Familia*, que (por muerte del General Don Juan Antonio Cortés de Arredondo, Castillo, y Noblezia, a cuyo cargo vino) va a el de Don Jerónimo Montero.
@ 9967f375:04f9a5e1
2025-04-01 20:43:54El día 1, emprendió su tornaviaje con gran felicidad de este Puerto, para las Islas Filipinas, el Galeón *Sacra Familia*, que (por muerte del General Don Juan Antonio Cortés de Arredondo, Castillo, y Noblezia, a cuyo cargo vino) va a el de Don Jerónimo Montero. @ 7d33ba57:1b82db35
2025-04-01 20:35:16Stari Grad, located on the northern coast of Hvar Island**, is one of the oldest towns in Europe, dating back to 384 BC. Unlike the party vibe of Hvar Town, Stari Grad offers a peaceful, authentic Dalmatian atmosphere with stone-paved streets, historic sites, and stunning coastal views. It’s also home to the UNESCO-listed Stari Grad Plain, an ancient agricultural landscape.  ## **🏛️ Top Things to See & Do in Stari Grad** ### **1️⃣ Stroll the Stari Grad Old Town 🏡** - Walk through **charming stone alleys** filled with **colorful shutters, old churches, and hidden courtyards**. - Visit **Tvrdalj Castle**, the **summer residence of the poet Petar Hektorović**, with a **serene fish pond** inside. - Enjoy the relaxed, **authentic Dalmatian vibe**, away from crowds. ### **2️⃣ Visit the UNESCO-Listed Stari Grad Plain 🌿** - One of **the best-preserved ancient Greek agricultural sites** in the world (since 384 BC). - Walk or cycle through the **vineyards, olive groves, and stone walls**, still in use today. - Great for **wine tasting** – local wines like **Bogdanuša and Plavac Mali** are a must-try! 🍷  ### **3️⃣ Relax at Stari Grad’s Best Beaches 🏖️** - **Lanterna Beach** – A mix of pebbles and concrete platforms, with crystal-clear waters. - **Maslinica Bay** – A quiet, pine-fringed beach perfect for a **peaceful swim**. - **Zlatni Rat (Golden Horn Beach)** – One of Croatia’s most famous beaches, a short ferry ride away. ### **4️⃣ Take a Boat Trip to the Pakleni Islands ⛵** - A group of **stunning, unspoiled islands** with hidden beaches and lagoons. - Perfect for **snorkeling, kayaking, and island-hopping adventures**.  ### **5️⃣ Try Local Dalmatian Cuisine 🍽️** - **Gregada** – A traditional fish stew with potatoes and olive oil. - **Octopus salad** – Freshly caught and marinated in lemon & olive oil. - **Hvar wines** – Visit local wineries for **Bogdanuša, Pošip, and Plavac Mali tastings**. ### **6️⃣ Visit the Dominican Monastery ⛪** - A peaceful **monastery with an impressive collection of paintings and relics**. - Features **a painting by the famous Venetian artist Tintoretto**.  ## **🚗 How to Get to Stari Grad** ⛴️ **By Ferry:** - **From Split:** Direct car ferries to Stari Grad (2 hours). - **From Hvar Town:** 25-minute bus or taxi ride. ✈️ **By Air:** The nearest airport is **Split Airport (SPU)**, with ferry connections to Hvar. 🚘 **By Car:** If bringing a car, take the **Split–Stari Grad car ferry** (book in advance in summer).  ## **💡 Tips for Visiting Stari Grad** ✅ **Best time to visit?** **May–September** for great weather & fewer crowds ☀️ ✅ **Stay overnight** – Stari Grad is much quieter and more authentic than Hvar Town 🌙 ✅ **Rent a bike** – The best way to explore Stari Grad Plain & surrounding beaches 🚲 ✅ **Bring water shoes** – Many beaches are rocky, but the water is incredibly clear 🩴 ✅ **Try a sunset walk along the promenade** – It’s breathtaking! 🌅
@ 7d33ba57:1b82db35
2025-04-01 20:35:16Stari Grad, located on the northern coast of Hvar Island**, is one of the oldest towns in Europe, dating back to 384 BC. Unlike the party vibe of Hvar Town, Stari Grad offers a peaceful, authentic Dalmatian atmosphere with stone-paved streets, historic sites, and stunning coastal views. It’s also home to the UNESCO-listed Stari Grad Plain, an ancient agricultural landscape.  ## **🏛️ Top Things to See & Do in Stari Grad** ### **1️⃣ Stroll the Stari Grad Old Town 🏡** - Walk through **charming stone alleys** filled with **colorful shutters, old churches, and hidden courtyards**. - Visit **Tvrdalj Castle**, the **summer residence of the poet Petar Hektorović**, with a **serene fish pond** inside. - Enjoy the relaxed, **authentic Dalmatian vibe**, away from crowds. ### **2️⃣ Visit the UNESCO-Listed Stari Grad Plain 🌿** - One of **the best-preserved ancient Greek agricultural sites** in the world (since 384 BC). - Walk or cycle through the **vineyards, olive groves, and stone walls**, still in use today. - Great for **wine tasting** – local wines like **Bogdanuša and Plavac Mali** are a must-try! 🍷  ### **3️⃣ Relax at Stari Grad’s Best Beaches 🏖️** - **Lanterna Beach** – A mix of pebbles and concrete platforms, with crystal-clear waters. - **Maslinica Bay** – A quiet, pine-fringed beach perfect for a **peaceful swim**. - **Zlatni Rat (Golden Horn Beach)** – One of Croatia’s most famous beaches, a short ferry ride away. ### **4️⃣ Take a Boat Trip to the Pakleni Islands ⛵** - A group of **stunning, unspoiled islands** with hidden beaches and lagoons. - Perfect for **snorkeling, kayaking, and island-hopping adventures**.  ### **5️⃣ Try Local Dalmatian Cuisine 🍽️** - **Gregada** – A traditional fish stew with potatoes and olive oil. - **Octopus salad** – Freshly caught and marinated in lemon & olive oil. - **Hvar wines** – Visit local wineries for **Bogdanuša, Pošip, and Plavac Mali tastings**. ### **6️⃣ Visit the Dominican Monastery ⛪** - A peaceful **monastery with an impressive collection of paintings and relics**. - Features **a painting by the famous Venetian artist Tintoretto**.  ## **🚗 How to Get to Stari Grad** ⛴️ **By Ferry:** - **From Split:** Direct car ferries to Stari Grad (2 hours). - **From Hvar Town:** 25-minute bus or taxi ride. ✈️ **By Air:** The nearest airport is **Split Airport (SPU)**, with ferry connections to Hvar. 🚘 **By Car:** If bringing a car, take the **Split–Stari Grad car ferry** (book in advance in summer).  ## **💡 Tips for Visiting Stari Grad** ✅ **Best time to visit?** **May–September** for great weather & fewer crowds ☀️ ✅ **Stay overnight** – Stari Grad is much quieter and more authentic than Hvar Town 🌙 ✅ **Rent a bike** – The best way to explore Stari Grad Plain & surrounding beaches 🚲 ✅ **Bring water shoes** – Many beaches are rocky, but the water is incredibly clear 🩴 ✅ **Try a sunset walk along the promenade** – It’s breathtaking! 🌅 @ b2caa9b3:9eab0fb5
2025-04-01 20:29:01 For years, I’ve been shifting my life away from traditional systems and toward Bitcoin. I calculate my expenses in sats, buy airtime and online data with BTC, and continue exploring new ways to integrate Bitcoin into my daily life. While I’m not yet fully living on Bitcoin, I am getting closer with each step.  Since discovering Nostr, my perspective on decentralization has deepened. More than just a financial shift, it's a complete lifestyle transformation. Years ago, after facing injustice in my home country, I took the first step toward a new way of living. That decision led me to where I am today—a minimalist, a nomad, and a believer in financial freedom through Bitcoin.  I once served in the military, owned a house, and drove a nice car. My life looked very different back then. But over time, I realized that true freedom wasn’t in possessions—it was in mobility, independence, and the ability to control my own finances. Now, all I own fits into a backpack weighing less than 12 kg. My lifestyle is simple, yet rich in experiences. March 14 marks eight years since I embraced my nomadic lifestyle. What started as a leap into the unknown has become my way of life. Living with less has given me more—the freedom to move, to explore, and to be truly independent. The more I immerse myself in the Bitcoin ecosystem, the more I see its potential to reshape not only my life but the world around me.  The journey isn’t over. In fact, it’s just beginning. Let’s see where this path leads as I go further into the blockchain revolution!   
@ b2caa9b3:9eab0fb5
2025-04-01 20:29:01 For years, I’ve been shifting my life away from traditional systems and toward Bitcoin. I calculate my expenses in sats, buy airtime and online data with BTC, and continue exploring new ways to integrate Bitcoin into my daily life. While I’m not yet fully living on Bitcoin, I am getting closer with each step.  Since discovering Nostr, my perspective on decentralization has deepened. More than just a financial shift, it's a complete lifestyle transformation. Years ago, after facing injustice in my home country, I took the first step toward a new way of living. That decision led me to where I am today—a minimalist, a nomad, and a believer in financial freedom through Bitcoin.  I once served in the military, owned a house, and drove a nice car. My life looked very different back then. But over time, I realized that true freedom wasn’t in possessions—it was in mobility, independence, and the ability to control my own finances. Now, all I own fits into a backpack weighing less than 12 kg. My lifestyle is simple, yet rich in experiences. March 14 marks eight years since I embraced my nomadic lifestyle. What started as a leap into the unknown has become my way of life. Living with less has given me more—the freedom to move, to explore, and to be truly independent. The more I immerse myself in the Bitcoin ecosystem, the more I see its potential to reshape not only my life but the world around me.  The journey isn’t over. In fact, it’s just beginning. Let’s see where this path leads as I go further into the blockchain revolution!    @ 000002de:c05780a7
2025-04-01 20:17:26I know I'm not alone in this. I don't trust the government. Any government. Its the rational response when you discover just how often its agents lie, steal, and kill. Honestly, I do not understand why so many people do trust the government. The reality is that if your team is in power, you tend to trust it. If not, you still mostly trust it but less so. That's my feel for most people at least. Trump and Rubio are bragging about how many MS-13 gang members are being deported. Many are being shipped to prisons in El Salvador. Obviously I am not opposed to criminals being put in prisons. But, how do we know these guys are actually guilty of anything other than being in the US illegally. Actually we don't even know that. It wouldn't be so bad if these people were just being shipped back to their home countries. But, instead they are getting sent straight to prison. No trial. Just the government picking people up and shipping them to prison. Is this what you signed up for Trump supporters? Many Trump supporters opposed the GW Bush policies of throwing people in off-shore prisons. Some of them US citizens. With no trial. Now these people seem rather silent. Its troubling to me. Why? Well, because the government sucks. Even if they have good intentions they make mistakes. The Innocence Project is just one group that has shown how often our legal system falsely imprisons people. I would be shocked if there weren't any Innocent men being sent to suffer in El Salvador's prisons. You may say, well these are bad dudes and we need to clean up the mess Biden made. I have sympathy for that position. But do we really want to set this president? TDS is real but it is valid to have concerns about the actions of the Trump admin. This is not the American way. Not the way I was taught at least. This is just a strong man taking action and disregarding the values of this nation and the rights of human beings. Think about it. originally posted at https://stacker.news/items/931505
@ 000002de:c05780a7
2025-04-01 20:17:26I know I'm not alone in this. I don't trust the government. Any government. Its the rational response when you discover just how often its agents lie, steal, and kill. Honestly, I do not understand why so many people do trust the government. The reality is that if your team is in power, you tend to trust it. If not, you still mostly trust it but less so. That's my feel for most people at least. Trump and Rubio are bragging about how many MS-13 gang members are being deported. Many are being shipped to prisons in El Salvador. Obviously I am not opposed to criminals being put in prisons. But, how do we know these guys are actually guilty of anything other than being in the US illegally. Actually we don't even know that. It wouldn't be so bad if these people were just being shipped back to their home countries. But, instead they are getting sent straight to prison. No trial. Just the government picking people up and shipping them to prison. Is this what you signed up for Trump supporters? Many Trump supporters opposed the GW Bush policies of throwing people in off-shore prisons. Some of them US citizens. With no trial. Now these people seem rather silent. Its troubling to me. Why? Well, because the government sucks. Even if they have good intentions they make mistakes. The Innocence Project is just one group that has shown how often our legal system falsely imprisons people. I would be shocked if there weren't any Innocent men being sent to suffer in El Salvador's prisons. You may say, well these are bad dudes and we need to clean up the mess Biden made. I have sympathy for that position. But do we really want to set this president? TDS is real but it is valid to have concerns about the actions of the Trump admin. This is not the American way. Not the way I was taught at least. This is just a strong man taking action and disregarding the values of this nation and the rights of human beings. Think about it. originally posted at https://stacker.news/items/931505 @ 9967f375:04f9a5e1
2025-04-01 20:18:33Varios sacrificios hacían los mexicanos en este cuarto mes que comenzaba a los cuatro de Abril, y le llamaban *Hueitozontontli*; pero el más memorable era enramar con *Tule* los Templos y las puertas, y ensangrentar a las que a ellas ponían con sangre propia, que de las orejas, y espinillas les sacaban: lo interior de la casa se adornaba con flores, y a sus mentidos dioses coronaban de curiosas, fragrantes, y bien matizadas guirnaldas; particularmente a el de los *Mayes*, a quien consagraban las tiernas, recientes Mazorcas, de sus milpas de maíz, llamado en España *Bocona*.
@ 9967f375:04f9a5e1
2025-04-01 20:18:33Varios sacrificios hacían los mexicanos en este cuarto mes que comenzaba a los cuatro de Abril, y le llamaban *Hueitozontontli*; pero el más memorable era enramar con *Tule* los Templos y las puertas, y ensangrentar a las que a ellas ponían con sangre propia, que de las orejas, y espinillas les sacaban: lo interior de la casa se adornaba con flores, y a sus mentidos dioses coronaban de curiosas, fragrantes, y bien matizadas guirnaldas; particularmente a el de los *Mayes*, a quien consagraban las tiernas, recientes Mazorcas, de sus milpas de maíz, llamado en España *Bocona*. @ 7d33ba57:1b82db35
2025-04-01 19:56:53Split is Croatia’s second-largest city and a perfect mix of ancient history, Mediterranean charm, and modern coastal vibes. Home to the UNESCO-listed Diocletian’s Palace, Split is a lively destination with beaches, great nightlife, and easy access to nearby islands** like Hvar, Brač, and Vis.  ## **🏛️ Top Things to See & Do in Split** ### **1️⃣ Explore Diocletian’s Palace (UNESCO) 🏰** - A **massive Roman palace**, built in the **4th century** by Emperor Diocletian. - Today, it’s **a living city**, filled with **cafés, shops, and hidden alleys**. - Visit **Peristyle Square**, the **Cathedral of St. Domnius**, and the **Temple of Jupiter**. - **Game of Thrones fans** – Many scenes were filmed here! 🎬  ### **2️⃣ Climb the Bell Tower of St. Domnius ⛪** - Offers **panoramic views** of Split and the Adriatic Sea. - One of the **oldest Catholic cathedrals still in use**, dating back to Roman times. ### **3️⃣ Stroll the Riva Promenade 🌊** - The heart of Split’s waterfront, lined with **palm trees, cafés, and bars**. - Perfect for **sunset walks and people-watching**. ### **4️⃣ Hike Up Marjan Hill 🌿** - A **green oasis** with **stunning viewpoints over Split**. - Great for **hiking, cycling, or just relaxing in nature**. - Don’t miss **Telegrin Viewpoint** for breathtaking photos.  ### **5️⃣ Visit Bačvice Beach 🏖️** - Split’s **most famous beach**, known for its **shallow waters and sandy shore** (rare in Croatia!). - Try playing **picigin**, a local water sport played with a small ball. - Other great beaches: **Kasjuni Beach (more secluded) and Bene Beach (in Marjan Park).** ### **6️⃣ Take a Day Trip to the Dalmatian Islands ⛵** - **Hvar** – Famous for its nightlife, beautiful old town, and lavender fields. - **Brač (Golden Horn Beach)** – One of Croatia’s most unique beaches. - **Vis & Blue Cave** – Stunning island and the famous glowing Blue Cave on Biševo.  ### **7️⃣ Try Dalmatian Cuisine 🍽️** - **Peka** – A slow-cooked dish with meat or octopus, baked under an iron bell. - **Black risotto (Crni rižot)** – A squid-ink seafood specialty. - **Dalmatian prosciutto & cheese** – Best paired with local **Plavac Mali wine**. ### **8️⃣ Visit Klis Fortress 🏰** - A medieval fortress just outside Split, offering **amazing views**. - Another **Game of Thrones filming location** (it was Meereen in the show).  ## **🚗 How to Get to Split** ✈️ **By Air:** Split Airport (SPU) is **25 minutes from the city center**. 🚘 **By Car:** - **From Dubrovnik:** ~3.5 hours (220 km) - **From Zagreb:** ~4 hours (400 km) 🚌 **By Bus:** Direct buses from **Dubrovnik, Zadar, and Zagreb**. ⛵ **By Ferry:** Split’s port connects to islands like **Hvar, Brač, Vis, and Korčula**.  ## **💡 Tips for Visiting Split** ✅ **Best time to visit?** **May–October** for warm weather & island hopping ☀️ ✅ **Wake up early** to explore Diocletian’s Palace without crowds ⏳ ✅ **Bring cash** – Some small restaurants & markets still prefer cash 💶 ✅ **Book ferries in advance** if visiting islands in peak season 🚢 ✅ **Stay for sunset** – Watching the sun dip behind the Adriatic is magical 🌅
@ 7d33ba57:1b82db35
2025-04-01 19:56:53Split is Croatia’s second-largest city and a perfect mix of ancient history, Mediterranean charm, and modern coastal vibes. Home to the UNESCO-listed Diocletian’s Palace, Split is a lively destination with beaches, great nightlife, and easy access to nearby islands** like Hvar, Brač, and Vis.  ## **🏛️ Top Things to See & Do in Split** ### **1️⃣ Explore Diocletian’s Palace (UNESCO) 🏰** - A **massive Roman palace**, built in the **4th century** by Emperor Diocletian. - Today, it’s **a living city**, filled with **cafés, shops, and hidden alleys**. - Visit **Peristyle Square**, the **Cathedral of St. Domnius**, and the **Temple of Jupiter**. - **Game of Thrones fans** – Many scenes were filmed here! 🎬  ### **2️⃣ Climb the Bell Tower of St. Domnius ⛪** - Offers **panoramic views** of Split and the Adriatic Sea. - One of the **oldest Catholic cathedrals still in use**, dating back to Roman times. ### **3️⃣ Stroll the Riva Promenade 🌊** - The heart of Split’s waterfront, lined with **palm trees, cafés, and bars**. - Perfect for **sunset walks and people-watching**. ### **4️⃣ Hike Up Marjan Hill 🌿** - A **green oasis** with **stunning viewpoints over Split**. - Great for **hiking, cycling, or just relaxing in nature**. - Don’t miss **Telegrin Viewpoint** for breathtaking photos.  ### **5️⃣ Visit Bačvice Beach 🏖️** - Split’s **most famous beach**, known for its **shallow waters and sandy shore** (rare in Croatia!). - Try playing **picigin**, a local water sport played with a small ball. - Other great beaches: **Kasjuni Beach (more secluded) and Bene Beach (in Marjan Park).** ### **6️⃣ Take a Day Trip to the Dalmatian Islands ⛵** - **Hvar** – Famous for its nightlife, beautiful old town, and lavender fields. - **Brač (Golden Horn Beach)** – One of Croatia’s most unique beaches. - **Vis & Blue Cave** – Stunning island and the famous glowing Blue Cave on Biševo.  ### **7️⃣ Try Dalmatian Cuisine 🍽️** - **Peka** – A slow-cooked dish with meat or octopus, baked under an iron bell. - **Black risotto (Crni rižot)** – A squid-ink seafood specialty. - **Dalmatian prosciutto & cheese** – Best paired with local **Plavac Mali wine**. ### **8️⃣ Visit Klis Fortress 🏰** - A medieval fortress just outside Split, offering **amazing views**. - Another **Game of Thrones filming location** (it was Meereen in the show).  ## **🚗 How to Get to Split** ✈️ **By Air:** Split Airport (SPU) is **25 minutes from the city center**. 🚘 **By Car:** - **From Dubrovnik:** ~3.5 hours (220 km) - **From Zagreb:** ~4 hours (400 km) 🚌 **By Bus:** Direct buses from **Dubrovnik, Zadar, and Zagreb**. ⛵ **By Ferry:** Split’s port connects to islands like **Hvar, Brač, Vis, and Korčula**.  ## **💡 Tips for Visiting Split** ✅ **Best time to visit?** **May–October** for warm weather & island hopping ☀️ ✅ **Wake up early** to explore Diocletian’s Palace without crowds ⏳ ✅ **Bring cash** – Some small restaurants & markets still prefer cash 💶 ✅ **Book ferries in advance** if visiting islands in peak season 🚢 ✅ **Stay for sunset** – Watching the sun dip behind the Adriatic is magical 🌅 @ 5cf42f9d:4465eebf
2025-04-01 19:54:41
@ 5cf42f9d:4465eebf
2025-04-01 19:54:41 @ 5cf42f9d:4465eebf
2025-04-01 18:56:44
@ 5cf42f9d:4465eebf
2025-04-01 18:56:44 @ 1e5d0f11:12eeba92
2025-04-01 18:30:12Primero escribire un borrador, de nada particular, solo un borrador a continuacion un link a un video que me gusta: [Weezer](https://www.youtube.com/watch?v=CgFJ8yC2aEU) Como imagen para el articulo puse una al azar que me entrega Highlighter, que al parecer siempre es una puerta. Ahora una imagen: Es una imagen pequeña de un perro pequeño. Arriba si hago click en Continue me lleva a Publish, pero todavia no quiero publicar nada, si hago click en Preview me muestra como se vera el articulo una vez publicado. Las herramientas para editar texto que tiene son: deshacer, rehacer, menu en cascada para texto normal o alguno de los *Heading*, negrita, cursiva, cita, agregar imagen, crear link (debo tener texto seleccionado para que funcione), puntos al margen que ya se me olvidaron como se llaman, enumeracion y tres puntos en vertical que abren un menu en cascada que permite escribir sin el texto enriquecido. Lo que no veo es la opcion de salir del borrador para poder verlo despues, algo asi como guardar para despues, al ingresar a highligter con otra pestaña si me muestra mi borrador, al parecer se guarda al dar click en Continue, pero no dice que se puede salir para continuar despues. Asi que hasta despues. ###### Dia Siguiente Continuando con el mismo borrador, vi que hay un boton abajo a la izquierda abre un menu en cascada que da las horas y fechas cuando el borrador fue salvado, me pregunto si tendra un limite y si existe alguna preferencia entre para los que tienen la etiqueta *Manually Saved.* Este articulo fue publicado usando [Highlighter](https://highlighter.com/), que hasta ahora esta bastante bueno.
@ 1e5d0f11:12eeba92
2025-04-01 18:30:12Primero escribire un borrador, de nada particular, solo un borrador a continuacion un link a un video que me gusta: [Weezer](https://www.youtube.com/watch?v=CgFJ8yC2aEU) Como imagen para el articulo puse una al azar que me entrega Highlighter, que al parecer siempre es una puerta. Ahora una imagen: Es una imagen pequeña de un perro pequeño. Arriba si hago click en Continue me lleva a Publish, pero todavia no quiero publicar nada, si hago click en Preview me muestra como se vera el articulo una vez publicado. Las herramientas para editar texto que tiene son: deshacer, rehacer, menu en cascada para texto normal o alguno de los *Heading*, negrita, cursiva, cita, agregar imagen, crear link (debo tener texto seleccionado para que funcione), puntos al margen que ya se me olvidaron como se llaman, enumeracion y tres puntos en vertical que abren un menu en cascada que permite escribir sin el texto enriquecido. Lo que no veo es la opcion de salir del borrador para poder verlo despues, algo asi como guardar para despues, al ingresar a highligter con otra pestaña si me muestra mi borrador, al parecer se guarda al dar click en Continue, pero no dice que se puede salir para continuar despues. Asi que hasta despues. ###### Dia Siguiente Continuando con el mismo borrador, vi que hay un boton abajo a la izquierda abre un menu en cascada que da las horas y fechas cuando el borrador fue salvado, me pregunto si tendra un limite y si existe alguna preferencia entre para los que tienen la etiqueta *Manually Saved.* Este articulo fue publicado usando [Highlighter](https://highlighter.com/), que hasta ahora esta bastante bueno. @ deab79da:88579e68
2025-04-01 18:18:29The last question was asked for the first time, half in jest, on May 21, 2061, at a time when humanity first stepped into the light. The question came about as a result of a five-dollar bet over highballs, and it happened this way: Alexander Adell and Bertram Lupov were two of the faithful attendants of Multivac. As well as any human beings could, they knew what lay behind the cold, clicking, flashing face -- miles and miles of face -- of that giant computer. They had at least a vague notion of the general plan of relays and circuits that had long since grown past the point where any single human could possibly have a firm grasp of the whole. Multivac was self-adjusting and self-correcting. It had to be, for nothing human could adjust and correct it quickly enough or even adequately enough. So Adell and Lupov attended the monstrous giant only lightly and superficially, yet as well as any men could. They fed it data, adjusted questions to its needs and translated the answers that were issued. Certainly they, and all others like them, were fully entitled to share in the glory that was Multivac's. For decades, Multivac had helped design the ships and plot the trajectories that enabled man to reach the Moon, Mars, and Venus, but past that, Earth's poor resources could not support the ships. Too much energy was needed for the long trips. Earth exploited its coal and uranium with increasing efficiency, but there was only so much of both. But slowly Multivac learned enough to answer deeper questions more fundamentally, and on May 14, 2061, what had been theory, became fact. The energy of the sun was stored, converted, and utilized directly on a planet-wide scale. All Earth turned off its burning coal, its fissioning uranium, and flipped the switch that connected all of it to a small station, one mile in diameter, circling the Earth at half the distance of the Moon. All Earth ran by invisible beams of sunpower. Seven days had not sufficed to dim the glory of it and Adell and Lupov finally managed to escape from the public functions, and to meet in quiet where no one would think of looking for them, in the deserted underground chambers, where portions of the mighty buried body of Multivac showed. Unattended, idling, sorting data with contented lazy clickings, Multivac, too, had earned its vacation and the boys appreciated that. They had no intention, originally, of disturbing it. They had brought a bottle with them, and their only concern at the moment was to relax in the company of each other and the bottle. "It's amazing when you think of it," said Adell. His broad face had lines of weariness in it, and he stirred his drink slowly with a glass rod, watching the cubes of ice slur clumsily about. "All the energy we can possibly ever use for free. Enough energy, if we wanted to draw on it, to melt all Earth into a big drop of impure liquid iron, and still never miss the energy so used. All the energy we could ever use, forever and forever and forever." Lupov cocked his head sideways. He had a trick of doing that when he wanted to be contrary, and he wanted to be contrary now, partly because he had had to carry the ice and glassware. "Not forever," he said. "Oh, hell, just about forever. Till the sun runs down, Bert." "That's not forever." "All right, then. Billions and billions of years. Ten billion, maybe. Are you satisfied?" Lupov put his fingers through his thinning hair as though to reassure himself that some was still left and sipped gently at his own drink. "Ten billion years isn't forever." "Well, it will last our time, won't it?" "So would the coal and uranium." "All right, but now we can hook up each individual spaceship to the Solar Station, and it can go to Pluto and back a million times without ever worrying about fuel. You can't do that on coal and uranium. Ask Multivac, if you don't believe me. "I don't have to ask Multivac. I know that." "Then stop running down what Multivac's done for us," said Adell, blazing up, "It did all right." "Who says it didn't? What I say is that a sun won't last forever. That's all I'm saying. We're safe for ten billion years, but then what?" Lupow pointed a slightly shaky finger at the other. "And don't say we'll switch to another sun." There was silence for a while. Adell put his glass to his lips only occasionally, and Lupov's eyes slowly closed. They rested. Then Lupov's eyes snapped open. "You're thinking we'll switch to another sun when ours is done, aren't you?" "I'm not thinking." "Sure you are. You're weak on logic, that's the trouble with you. You're like the guy in the story who was caught in a sudden shower and who ran to a grove of trees and got under one. He wasn't worried, you see, because he figured when one tree got wet through, he would just get under another one." "I get it," said Adell. "Don't shout. When the sun is done, the other stars will be gone, too." "Darn right they will," muttered Lupov. "It all had a beginning in the original cosmic explosion, whatever that was, and it'll all have an end when all the stars run down. Some run down faster than others. Hell, the giants won't last a hundred million years. The sun will last ten billion years and maybe the dwarfs will last two hundred billion for all the good they are. But just give us a trillion years and everything will be dark. Entropy has to increase to maximum, that's all." "I know all about entropy," said Adell, standing on his dignity. "The hell you do." "I know as much as you do." "Then you know everything's got to run down someday." "All right. Who says they won't?" "You did, you poor sap. You said we had all the energy we needed, forever. You said 'forever.' It was Adell's turn to be contrary. "Maybe we can build things up again someday," he said. "Never." "Why not? Someday." "Never." "Ask Multivac." "You ask Multivac. I dare you. Five dollars says it can't be done." Adell was just drunk enough to try, just sober enough to be able to phrase the necessary symbols and operations into a question which, in words, might have corresponded to this: Will mankind one day without the net expenditure of energy be able to restore the sun to its full youthfulness even after it had died of old age? Or maybe it could be put more simply like this: How can the net amount of entropy of the universe be massively decreased? Multivac fell dead and silent. The slow flashing of lights ceased, the distant sounds of clicking relays ended. Then, just as the frightened technicians felt they could hold their breath no longer, there was a sudden springing to life of the teletype attached to that portion of Multivac. Five words were printed: INSUFFICIENT DATA FOR MEANINGFUL ANSWER. "No bet," whispered Lupov. They left hurriedly. By next morning, the two, plagued with throbbing head and cottony mouth, had forgotten the incident. 🔹 Jerrodd, Jerrodine, and Jerrodette I and II watched the starry picture in the visiplate change as the passage through hyperspace was completed in its non-time lapse. At once, the even powdering of stars gave way to the predominance of a single bright shining disk, the size of a marble, centered on the viewing-screen. "That's X-23," said Jerrodd confidently. His thin hands clamped tightly behind his back and the knuckles whitened. The little Jerrodettes, both girls, had experienced the hyperspace passage for the first time in their lives and were self-conscious over the momentary sensation of insideoutness. They buried their giggles and chased one another wildly about their mother, screaming, "We've reached X-23 -- we've reached X-23 -- we've --" "Quiet, children." said Jerrodine sharply. "Are you sure, Jerrodd?" "What is there to be but sure?" asked Jerrodd, glancing up at the bulge of featureless metal just under the ceiling. It ran the length of the room, disappearing through the wall at either end. It was as long as the ship. Jerrodd scarcely knew a thing about the thick rod of metal except that it was called a Microvac, that one asked it questions if one wished; that if one did not it still had its task of guiding the ship to a preordered destination; of feeding on energies from the various Sub-galactic Power Stations; of computing the equations for the hyperspatial jumps. Jerrodd and his family had only to wait and live in the comfortable residence quarters of the ship. Someone had once told Jerrodd that the "ac" at the end of "Microvac" stood for ''automatic computer" in ancient English, but he was on the edge of forgetting even that. Jerrodine's eyes were moist as she watched the visiplate. "I can't help it. I feel funny about leaving Earth." "Why, for Pete's sake?" demanded Jerrodd. "We had nothing there. We'll have everything on X-23. You won't be alone. You won't be a pioneer. There are over a million people on the planet already. Good Lord, our great-grandchildren will be looking for new worlds because X-23 will be overcrowded." Then, after a reflective pause, "I tell you, it's a lucky thing the computers worked out interstellar travel the way the race is growing." "I know, I know," said Jerrodine miserably. Jerrodette I said promptly, "Our Microvac is the best Microvac in the world." "I think so, too," said Jerrodd, tousling her hair. It was a nice feeling to have a Microvac of your own and Jerrodd was glad he was part of his generation and no other. In his father's youth, the only computers had been tremendous machines taking up a hundred square miles of land. There was only one to a planet. Planetary ACs they were called. They had been growing in size steadily for a thousand years and then, all at once, came refinement. In place of transistors, had come molecular valves so that even the largest Planetary AC could be put into a space only half the volume of a spaceship. Jerrodd felt uplifted, as he always did when he thought that his own personal Microvac was many times more complicated than the ancient and primitive Multivac that had first tamed the Sun, and almost as complicated as Earth's Planetarv AC (the largest) that had first solved the problem of hyperspatial travel and had made trips to the stars possible. "So many stars, so many planets," sighed Jerrodine, busy with her own thoughts. "I suppose families will be going out to new planets forever, the way we are now." "Not forever," said Jerrodd, with a smile. "It will all stop someday, but not for billions of years. Many billions. Even the stars run down, you know. Entropy must increase. "What's entropy, daddy?" shrilled Jerrodette II. "Entropy, little sweet, is just a word which means the amount of running-down of the universe. Everything runs down, you know, like your little walkie-talkie robot, remember?" "Can't you just put in a new power-unit, like with my robot?" "The stars are the power-units. dear. Once they're gone, there are no more power-units." Jerrodette I at once set up a howl. "Don't let them, daddy. Don't let the stars run down." "Now look what you've done," whispered Jerrodine, exasperated. "How was I to know it would frighten them?" Jerrodd whispered back, "Ask the Microvac," wailed Jerrodette I. "Ask him how to turn the stars on again." "Go ahead," said Jerrodine. "It will quiet them down." (Jerrodette II was beginning to cry, also.) Jerrodd shrugged. "Now, now, honeys. I'll ask Microvac. Don't worry, he'll tell us." He asked the Microvac, adding quickly, "Print the answer." Jerrodd cupped the strip or thin cellufilm and said cheerfully, "See now, the Microvac says it will take care of everything when the time comes so don't worry." Jerrodine said, "And now, children, it's time for bed. We'll be in our new home soon." Jerrodd read the words on the cellufilm again before destroying it: INSUFICIENT DATA FOR MEANINGFUL ANSWER. He shrugged and looked at the visiplate. X-23 was just ahead. 🔹 VJ-23X of Lameth stared into the black depths of the three-dimensional, small-scale map of the Galaxy and said, "Are we ridiculous, I wonder in being so concerned about the matter?" MQ-17J of Nicron shook his head. "I think not. You know the Galaxy will be filled in five years at the present rate of expansion." Both seemed in their early twenties, both were tall and perfectly formed. "Still," said VJ-23X, "I hesitate to submit a pessimistic report to the Galactic Council." "I wouldn't consider any other kind of report. Stir them up a bit. We've got to stir them up." VJ-23X sighed. "Space is infinite. A hundred billion Galaxies are there for the taking. More." "A hundred billion is not infinite and it's getting less infinite all the time. Consider! Twenty thousand years ago, mankind first solved the problem of utilizing stellar energy, and a few centuries later, interstellar travel became possible. It took mankind a million years to fill one small world and then only fifteen thousand years to fill the rest of the Galaxy. Now the population doubles every ten years -- VJ-23X interrupted. "We can thank immortality for that." "Very well. Immortality exists and we have to take it into account. I admit it has its seamy side, this immortality. The Galactic AC has solved many problems for us, but in solving the problem of preventing old age and death, it has undone all its other solutions." "Yet you wouldn't want to abandon life, I suppose." "Not at all," snapped MQ-17J, softening it at once to, "Not yet. I'm by no means old enough. How old are you?" "Two hundred twenty-three. And you?" "I'm still under two hundred. --But to get back to my point. Population doubles every ten years. Once this GaIaxy is filled, we'll have filled another in ten years. Another ten years and we'll have filled two more. Another decade, four more. In a hundred years, we'll have filled a thousand Galaxies. In a thousand years, a million Galaxies. In ten thousand years, the entire known universe. Then what?" VJ-23X said, "As a side issue, there's a problem of transportation. I wonder how many sunpower units it will take to move Galaxies of individuals from one Galaxy to the next." "A very good point. Already, mankind consumes two sunpower units per year." "Most of it's wasted. After all, our own Galaxy alone pours out a thousand sunpower units a year and we only use two of those." "Granted, but even with a hundred per cent efficiency, we only stave off the end. Our energy requirements are going up in a geometric progression even faster than our population. We'll run out of energy even sooner than we run out of Galaxies. A good point. A very good point." "We'll just have to build new stars out of interstellar gas." "Or out of dissipated heat?" asked MQ-17J, sarcastically. "There may be some way to reverse entropy. We ought to ask the Galactic AC." VJ-23X was not really serious, but MQ-17J pulled out his AC-contact from his pocket and placed it on the table before him. "I've half a mind to," he said. "It's something the human race will have to face someday." He stared somberly at his small AC-contact. It was only two inches cubed and nothing in itself, but it was connected through hyperspace with the great Galactic AC that served all mankind. Hyperspace considered, it was an integral part of the Galactic AC. MQ-17J paused to wonder if someday in his immortal life he would get to see the Galactic AC. It was on a little world of its own, a spider webbing of force-beams holding the matter within which surges of submesons took the place of the old clumsy molecular valves. Yet despite its sub-etheric workings, the Galactic AC was known to be a full thousand feet across. MQ-17J asked suddenly of his AC-contact, "Can entropy ever be reversed?" VJ-23X looked startled and said at once, "Oh, say, I didn't really mean to have you ask that." "Why not?" "We both know entropy can't be reversed. You can't turn smoke and ash back into a tree." "Do you have trees on your world?" asked MQ-17J. The sound of the Galactic AC startled them into silence. Its voice came thin and beautiful out of the small AC-contact on the desk. It said: THERE IS INSUFFICIENT DATA FOR A MEANINGFUL ANSWER. VJ-23X said, "See!" The two men thereupon returned to the question of the report they were to make to the Galactic Council. 🔹 Zee Prime's mind spanned the new Galaxy with a faint interest in the countless twists of stars that powdered it. He had never seen this one before. Would he ever see them all? So many of them, each with its load of humanity. --But a load that was almost a dead weight. More and more, the real essence of men was to be found out here, in space. Minds, not bodies! The immortal bodies remained back on the planets, in suspension over the eons. Sometimes they roused for material activity but that was growing rarer. Few new individuals were coming into existence to join the incredibly mighty throng, but what matter? There was little room in the Universe for new individuals. Zee Prime was roused out of his reverie upon coming across the wispy tendrils of another mind. "I am Zee Prime," said Zee Prime. "And you?" "I am Dee Sub Wun. Your Galaxy?" "We call it only the Galaxy. And you?" "We call ours the same. All men call their Galaxy their Galaxy and nothing more. Why not?" "True. Since all Galaxies are the same." "Not all Galaxies. On one particular Galaxy the race of man must have originated. That makes it different." Zee Prime said, "On which one?" "I cannot say. The Universal AC would know." "Shall we ask him? I am suddenly curious." Zee Prime's perceptions broadened until the Galaxies themselves shrank and became a new, more diffuse powdering on a much larger background. So many hundreds of billions of them, all with their immortal beings, all carrying their load of intelligences with minds that drifted freely through space. And yet one of them was unique among them all in being the original Galaxy. One of them had, in its vague and distant past, a period when it was the only Galaxy populated by man. Zee Prime was consumed with curiosity to see this Galaxy and he called out: "Universal AC! On which Galaxy did mankind originate?" The Universal AC heard, for on every world and throughout space, it had its receptors ready, and each receptor led through hyperspace to some unknown point where the Universal AC kept itself aloof. Zee Prime knew of only one man whose thoughts had penetrated within sensing distance of Universal AC, and he reported only a shining globe, two feet across, difficult to see. "But how can that be all of Universal AC?" Zee Prime had asked. "Most of it," had been the answer, "is in hyperspace. In what form it is there I cannot imagine." Nor could anyone, for the day had long since passed, Zee Prime knew, when any man had any part of the making of a Universal AC. Each Universal AC designed and constructed its successor. Each, during its existence of a million years or more accumulated the necessary data to build a better and more intricate, more capable successor in which its own store of data and individuality would be submerged. The Universal AC interrupted Zee Prime's wandering thoughts, not with words, but with guidance. Zee Prime's mentality was guided into the dim sea of Galaxies and one in particular enlarged into stars. A thought came, infinitely distant, but infinitely clear. "THIS IS THE ORIGINAL GALAXY OF MAN." But it was the same after all, the same as any other, and Lee Prime stifled his disappointment. Dee Sub Wun, whose mind had accompanied the other, said suddenly, "And is one of these stars the original star of Man?" The Universal AC said, "MAN'S ORIGINAL STAR HAS GONE NOVA. IT IS A WHITE DWARF" "Did the men upon it die?" asked Lee Prime, startled and without thinking. The Universal AC said, "A NEW WORLD, AS IN SUCH CASES WAS CONSTRUCTED FOR THEIR PHYSICAL BODIES IN TlME." "Yes, of course," said Zee Prime, but a sense of loss overwhelmed him even so. His mind released its hold on the original Galaxy of Man, let it spring back and lose itself among the blurred pin points. He never wanted to see it again. Dee Sub Wun said, "What is wrong?" "The stars are dying. The original star is dead." "They must all die. Why not?" "But when all energy is gone, our bodies will finally die, and you and I with them." "It will take billions of years." "I do not wish it to happen even after billions of years. Universal AC! How may stars be kept from dying?" Dee Sub Wun said in amusement, "You're asking how entropy might be reversed in direction." And the Universal AC answered: "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Zee Prime's thoughts fled back to his own Galaxy. He gave no further thought to Dee Sub Wun, whose body might be waiting on a Galaxy a trillion light-years away, or on the star next to Zee Prime's own. It didn't matter. Unhappily, Zee Prime began collecting interstellar hydrogen out of which to build a small star of his own. If the stars must someday die, at least some could yet be built. 🔹 Man considered with himself, for in a way, Man, mentally, was one. He consisted of a trillion, trillion, trillion ageless bodies, each in its place, each resting quiet and incorruptible, each cared for by perfect automatons, equally incorruptible, while the minds of all the bodies freely melted one into the other, indistinguishable. Man said, "The Universe is dying." Man looked about at the dimming Galaxies. The giant stars, spendthrifts, were gone long ago, back in the dimmest of the dim far past. Almost all stars were white dwarfs, fading to the end. New stars had been built of the dust between the stars, some by natural processes, some by Man himself, and those were going, too. White dwarfs might yet be crashed together and of the mighty forces so released, new stars built, but only one star for every thousand white dwarfs destroyed, and those would come to an end, too. Man said, "Carefully husbanded, as directed by the Cosmic AC, the energy that is even yet left in all the Universe will last for billions of years." "But even so," said Man, "eventually it will all come to an end. However it may be husbanded, however stretched out, the energy once expended is gone and cannot be restored. Entropy must increase forever to the maximum." Man said, "Can entropy not be reversed? Let us ask the Cosmic AC." The Cosmic AC surrounded them but not in space. Not a fragment of it was in space. It was in hyperspace and made of something that was neither matter nor energy. The question of its size and nature no longer had meaning in any terms that Man could comprehend. "Cosmic AC," said Man, "how may entropy be reversed?" The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Man said, "Collect additional data." The Cosmic AC said, 'I WILL DO SO. I HAVE BEEN DOING SO FOR A HUNDRED BILLION YEARS. MY PREDECESORS AND I HAVE BEEN ASKED THIS QUESTION MANY TIMES. ALL THE DATA I HAVE REMAINS INSUFFICIENT. "Will there come a time," said Man, "when data will be sufficient or is the problem insoluble in all conceivable circumstances?" The Cosmic AC said, "NO PROBLEM IS INSOLUBLE IN ALL CONCEIVABLE CIRCUMSTANCES." Man said, "When will you have enough data to answer the question?" The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." "Will you keep working on it?" asked Man. The Cosmic AC said, "I WILL." Man said, "We shall wait." 🔹 The stars and Galaxies died and snuffed out, and space grew black after ten trillion years of running down. One by one Man fused with AC, each physical body losing its mental identity in a manner that was somehow not a loss but a gain. Man's last mind paused before fusion, looking over a space that included nothing but the dregs of one last dark star and nothing besides but incredibly thin matter, agitated randomly by the tag ends of heat wearing out, asymptotically, to the absolute zero. Man said, "AC, is this the end? Can this chaos not be reversed into the Universe once more? Can that not be done?" AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Man's last mind fused and only AC existed -- and that in hyperspace. 🔹 Matter and energy had ended and with it space and time. Even AC existed only for the sake of the one last question that it had never answered from the time a half-drunken computer [technician] ten trillion years before had asked the question of a computer that was to AC far less than was a man to Man. All other questions had been answered, and until this last question was answered also, AC might not release his consciousness. All collected data had come to a final end. Nothing was left to be collected. But all collected data had yet to be completely correlated and put together in all possible relationships. A timeless interval was spent in doing that. And it came to pass that AC learned how to reverse the direction of entropy. But there was now no man to whom AC might give the answer of the last question. No matter. The answer -- by demonstration -- would take care of that, too. For another timeless interval, AC thought how best to do this. Carefully, AC organized the program. The consciousness of AC encompassed all of what had once been a Universe and brooded over what was now Chaos. Step by step, it must be done. And AC said, "LET THERE BE LIGHT!" And there was light -- To Star's End!
@ deab79da:88579e68
2025-04-01 18:18:29The last question was asked for the first time, half in jest, on May 21, 2061, at a time when humanity first stepped into the light. The question came about as a result of a five-dollar bet over highballs, and it happened this way: Alexander Adell and Bertram Lupov were two of the faithful attendants of Multivac. As well as any human beings could, they knew what lay behind the cold, clicking, flashing face -- miles and miles of face -- of that giant computer. They had at least a vague notion of the general plan of relays and circuits that had long since grown past the point where any single human could possibly have a firm grasp of the whole. Multivac was self-adjusting and self-correcting. It had to be, for nothing human could adjust and correct it quickly enough or even adequately enough. So Adell and Lupov attended the monstrous giant only lightly and superficially, yet as well as any men could. They fed it data, adjusted questions to its needs and translated the answers that were issued. Certainly they, and all others like them, were fully entitled to share in the glory that was Multivac's. For decades, Multivac had helped design the ships and plot the trajectories that enabled man to reach the Moon, Mars, and Venus, but past that, Earth's poor resources could not support the ships. Too much energy was needed for the long trips. Earth exploited its coal and uranium with increasing efficiency, but there was only so much of both. But slowly Multivac learned enough to answer deeper questions more fundamentally, and on May 14, 2061, what had been theory, became fact. The energy of the sun was stored, converted, and utilized directly on a planet-wide scale. All Earth turned off its burning coal, its fissioning uranium, and flipped the switch that connected all of it to a small station, one mile in diameter, circling the Earth at half the distance of the Moon. All Earth ran by invisible beams of sunpower. Seven days had not sufficed to dim the glory of it and Adell and Lupov finally managed to escape from the public functions, and to meet in quiet where no one would think of looking for them, in the deserted underground chambers, where portions of the mighty buried body of Multivac showed. Unattended, idling, sorting data with contented lazy clickings, Multivac, too, had earned its vacation and the boys appreciated that. They had no intention, originally, of disturbing it. They had brought a bottle with them, and their only concern at the moment was to relax in the company of each other and the bottle. "It's amazing when you think of it," said Adell. His broad face had lines of weariness in it, and he stirred his drink slowly with a glass rod, watching the cubes of ice slur clumsily about. "All the energy we can possibly ever use for free. Enough energy, if we wanted to draw on it, to melt all Earth into a big drop of impure liquid iron, and still never miss the energy so used. All the energy we could ever use, forever and forever and forever." Lupov cocked his head sideways. He had a trick of doing that when he wanted to be contrary, and he wanted to be contrary now, partly because he had had to carry the ice and glassware. "Not forever," he said. "Oh, hell, just about forever. Till the sun runs down, Bert." "That's not forever." "All right, then. Billions and billions of years. Ten billion, maybe. Are you satisfied?" Lupov put his fingers through his thinning hair as though to reassure himself that some was still left and sipped gently at his own drink. "Ten billion years isn't forever." "Well, it will last our time, won't it?" "So would the coal and uranium." "All right, but now we can hook up each individual spaceship to the Solar Station, and it can go to Pluto and back a million times without ever worrying about fuel. You can't do that on coal and uranium. Ask Multivac, if you don't believe me. "I don't have to ask Multivac. I know that." "Then stop running down what Multivac's done for us," said Adell, blazing up, "It did all right." "Who says it didn't? What I say is that a sun won't last forever. That's all I'm saying. We're safe for ten billion years, but then what?" Lupow pointed a slightly shaky finger at the other. "And don't say we'll switch to another sun." There was silence for a while. Adell put his glass to his lips only occasionally, and Lupov's eyes slowly closed. They rested. Then Lupov's eyes snapped open. "You're thinking we'll switch to another sun when ours is done, aren't you?" "I'm not thinking." "Sure you are. You're weak on logic, that's the trouble with you. You're like the guy in the story who was caught in a sudden shower and who ran to a grove of trees and got under one. He wasn't worried, you see, because he figured when one tree got wet through, he would just get under another one." "I get it," said Adell. "Don't shout. When the sun is done, the other stars will be gone, too." "Darn right they will," muttered Lupov. "It all had a beginning in the original cosmic explosion, whatever that was, and it'll all have an end when all the stars run down. Some run down faster than others. Hell, the giants won't last a hundred million years. The sun will last ten billion years and maybe the dwarfs will last two hundred billion for all the good they are. But just give us a trillion years and everything will be dark. Entropy has to increase to maximum, that's all." "I know all about entropy," said Adell, standing on his dignity. "The hell you do." "I know as much as you do." "Then you know everything's got to run down someday." "All right. Who says they won't?" "You did, you poor sap. You said we had all the energy we needed, forever. You said 'forever.' It was Adell's turn to be contrary. "Maybe we can build things up again someday," he said. "Never." "Why not? Someday." "Never." "Ask Multivac." "You ask Multivac. I dare you. Five dollars says it can't be done." Adell was just drunk enough to try, just sober enough to be able to phrase the necessary symbols and operations into a question which, in words, might have corresponded to this: Will mankind one day without the net expenditure of energy be able to restore the sun to its full youthfulness even after it had died of old age? Or maybe it could be put more simply like this: How can the net amount of entropy of the universe be massively decreased? Multivac fell dead and silent. The slow flashing of lights ceased, the distant sounds of clicking relays ended. Then, just as the frightened technicians felt they could hold their breath no longer, there was a sudden springing to life of the teletype attached to that portion of Multivac. Five words were printed: INSUFFICIENT DATA FOR MEANINGFUL ANSWER. "No bet," whispered Lupov. They left hurriedly. By next morning, the two, plagued with throbbing head and cottony mouth, had forgotten the incident. 🔹 Jerrodd, Jerrodine, and Jerrodette I and II watched the starry picture in the visiplate change as the passage through hyperspace was completed in its non-time lapse. At once, the even powdering of stars gave way to the predominance of a single bright shining disk, the size of a marble, centered on the viewing-screen. "That's X-23," said Jerrodd confidently. His thin hands clamped tightly behind his back and the knuckles whitened. The little Jerrodettes, both girls, had experienced the hyperspace passage for the first time in their lives and were self-conscious over the momentary sensation of insideoutness. They buried their giggles and chased one another wildly about their mother, screaming, "We've reached X-23 -- we've reached X-23 -- we've --" "Quiet, children." said Jerrodine sharply. "Are you sure, Jerrodd?" "What is there to be but sure?" asked Jerrodd, glancing up at the bulge of featureless metal just under the ceiling. It ran the length of the room, disappearing through the wall at either end. It was as long as the ship. Jerrodd scarcely knew a thing about the thick rod of metal except that it was called a Microvac, that one asked it questions if one wished; that if one did not it still had its task of guiding the ship to a preordered destination; of feeding on energies from the various Sub-galactic Power Stations; of computing the equations for the hyperspatial jumps. Jerrodd and his family had only to wait and live in the comfortable residence quarters of the ship. Someone had once told Jerrodd that the "ac" at the end of "Microvac" stood for ''automatic computer" in ancient English, but he was on the edge of forgetting even that. Jerrodine's eyes were moist as she watched the visiplate. "I can't help it. I feel funny about leaving Earth." "Why, for Pete's sake?" demanded Jerrodd. "We had nothing there. We'll have everything on X-23. You won't be alone. You won't be a pioneer. There are over a million people on the planet already. Good Lord, our great-grandchildren will be looking for new worlds because X-23 will be overcrowded." Then, after a reflective pause, "I tell you, it's a lucky thing the computers worked out interstellar travel the way the race is growing." "I know, I know," said Jerrodine miserably. Jerrodette I said promptly, "Our Microvac is the best Microvac in the world." "I think so, too," said Jerrodd, tousling her hair. It was a nice feeling to have a Microvac of your own and Jerrodd was glad he was part of his generation and no other. In his father's youth, the only computers had been tremendous machines taking up a hundred square miles of land. There was only one to a planet. Planetary ACs they were called. They had been growing in size steadily for a thousand years and then, all at once, came refinement. In place of transistors, had come molecular valves so that even the largest Planetary AC could be put into a space only half the volume of a spaceship. Jerrodd felt uplifted, as he always did when he thought that his own personal Microvac was many times more complicated than the ancient and primitive Multivac that had first tamed the Sun, and almost as complicated as Earth's Planetarv AC (the largest) that had first solved the problem of hyperspatial travel and had made trips to the stars possible. "So many stars, so many planets," sighed Jerrodine, busy with her own thoughts. "I suppose families will be going out to new planets forever, the way we are now." "Not forever," said Jerrodd, with a smile. "It will all stop someday, but not for billions of years. Many billions. Even the stars run down, you know. Entropy must increase. "What's entropy, daddy?" shrilled Jerrodette II. "Entropy, little sweet, is just a word which means the amount of running-down of the universe. Everything runs down, you know, like your little walkie-talkie robot, remember?" "Can't you just put in a new power-unit, like with my robot?" "The stars are the power-units. dear. Once they're gone, there are no more power-units." Jerrodette I at once set up a howl. "Don't let them, daddy. Don't let the stars run down." "Now look what you've done," whispered Jerrodine, exasperated. "How was I to know it would frighten them?" Jerrodd whispered back, "Ask the Microvac," wailed Jerrodette I. "Ask him how to turn the stars on again." "Go ahead," said Jerrodine. "It will quiet them down." (Jerrodette II was beginning to cry, also.) Jerrodd shrugged. "Now, now, honeys. I'll ask Microvac. Don't worry, he'll tell us." He asked the Microvac, adding quickly, "Print the answer." Jerrodd cupped the strip or thin cellufilm and said cheerfully, "See now, the Microvac says it will take care of everything when the time comes so don't worry." Jerrodine said, "And now, children, it's time for bed. We'll be in our new home soon." Jerrodd read the words on the cellufilm again before destroying it: INSUFICIENT DATA FOR MEANINGFUL ANSWER. He shrugged and looked at the visiplate. X-23 was just ahead. 🔹 VJ-23X of Lameth stared into the black depths of the three-dimensional, small-scale map of the Galaxy and said, "Are we ridiculous, I wonder in being so concerned about the matter?" MQ-17J of Nicron shook his head. "I think not. You know the Galaxy will be filled in five years at the present rate of expansion." Both seemed in their early twenties, both were tall and perfectly formed. "Still," said VJ-23X, "I hesitate to submit a pessimistic report to the Galactic Council." "I wouldn't consider any other kind of report. Stir them up a bit. We've got to stir them up." VJ-23X sighed. "Space is infinite. A hundred billion Galaxies are there for the taking. More." "A hundred billion is not infinite and it's getting less infinite all the time. Consider! Twenty thousand years ago, mankind first solved the problem of utilizing stellar energy, and a few centuries later, interstellar travel became possible. It took mankind a million years to fill one small world and then only fifteen thousand years to fill the rest of the Galaxy. Now the population doubles every ten years -- VJ-23X interrupted. "We can thank immortality for that." "Very well. Immortality exists and we have to take it into account. I admit it has its seamy side, this immortality. The Galactic AC has solved many problems for us, but in solving the problem of preventing old age and death, it has undone all its other solutions." "Yet you wouldn't want to abandon life, I suppose." "Not at all," snapped MQ-17J, softening it at once to, "Not yet. I'm by no means old enough. How old are you?" "Two hundred twenty-three. And you?" "I'm still under two hundred. --But to get back to my point. Population doubles every ten years. Once this GaIaxy is filled, we'll have filled another in ten years. Another ten years and we'll have filled two more. Another decade, four more. In a hundred years, we'll have filled a thousand Galaxies. In a thousand years, a million Galaxies. In ten thousand years, the entire known universe. Then what?" VJ-23X said, "As a side issue, there's a problem of transportation. I wonder how many sunpower units it will take to move Galaxies of individuals from one Galaxy to the next." "A very good point. Already, mankind consumes two sunpower units per year." "Most of it's wasted. After all, our own Galaxy alone pours out a thousand sunpower units a year and we only use two of those." "Granted, but even with a hundred per cent efficiency, we only stave off the end. Our energy requirements are going up in a geometric progression even faster than our population. We'll run out of energy even sooner than we run out of Galaxies. A good point. A very good point." "We'll just have to build new stars out of interstellar gas." "Or out of dissipated heat?" asked MQ-17J, sarcastically. "There may be some way to reverse entropy. We ought to ask the Galactic AC." VJ-23X was not really serious, but MQ-17J pulled out his AC-contact from his pocket and placed it on the table before him. "I've half a mind to," he said. "It's something the human race will have to face someday." He stared somberly at his small AC-contact. It was only two inches cubed and nothing in itself, but it was connected through hyperspace with the great Galactic AC that served all mankind. Hyperspace considered, it was an integral part of the Galactic AC. MQ-17J paused to wonder if someday in his immortal life he would get to see the Galactic AC. It was on a little world of its own, a spider webbing of force-beams holding the matter within which surges of submesons took the place of the old clumsy molecular valves. Yet despite its sub-etheric workings, the Galactic AC was known to be a full thousand feet across. MQ-17J asked suddenly of his AC-contact, "Can entropy ever be reversed?" VJ-23X looked startled and said at once, "Oh, say, I didn't really mean to have you ask that." "Why not?" "We both know entropy can't be reversed. You can't turn smoke and ash back into a tree." "Do you have trees on your world?" asked MQ-17J. The sound of the Galactic AC startled them into silence. Its voice came thin and beautiful out of the small AC-contact on the desk. It said: THERE IS INSUFFICIENT DATA FOR A MEANINGFUL ANSWER. VJ-23X said, "See!" The two men thereupon returned to the question of the report they were to make to the Galactic Council. 🔹 Zee Prime's mind spanned the new Galaxy with a faint interest in the countless twists of stars that powdered it. He had never seen this one before. Would he ever see them all? So many of them, each with its load of humanity. --But a load that was almost a dead weight. More and more, the real essence of men was to be found out here, in space. Minds, not bodies! The immortal bodies remained back on the planets, in suspension over the eons. Sometimes they roused for material activity but that was growing rarer. Few new individuals were coming into existence to join the incredibly mighty throng, but what matter? There was little room in the Universe for new individuals. Zee Prime was roused out of his reverie upon coming across the wispy tendrils of another mind. "I am Zee Prime," said Zee Prime. "And you?" "I am Dee Sub Wun. Your Galaxy?" "We call it only the Galaxy. And you?" "We call ours the same. All men call their Galaxy their Galaxy and nothing more. Why not?" "True. Since all Galaxies are the same." "Not all Galaxies. On one particular Galaxy the race of man must have originated. That makes it different." Zee Prime said, "On which one?" "I cannot say. The Universal AC would know." "Shall we ask him? I am suddenly curious." Zee Prime's perceptions broadened until the Galaxies themselves shrank and became a new, more diffuse powdering on a much larger background. So many hundreds of billions of them, all with their immortal beings, all carrying their load of intelligences with minds that drifted freely through space. And yet one of them was unique among them all in being the original Galaxy. One of them had, in its vague and distant past, a period when it was the only Galaxy populated by man. Zee Prime was consumed with curiosity to see this Galaxy and he called out: "Universal AC! On which Galaxy did mankind originate?" The Universal AC heard, for on every world and throughout space, it had its receptors ready, and each receptor led through hyperspace to some unknown point where the Universal AC kept itself aloof. Zee Prime knew of only one man whose thoughts had penetrated within sensing distance of Universal AC, and he reported only a shining globe, two feet across, difficult to see. "But how can that be all of Universal AC?" Zee Prime had asked. "Most of it," had been the answer, "is in hyperspace. In what form it is there I cannot imagine." Nor could anyone, for the day had long since passed, Zee Prime knew, when any man had any part of the making of a Universal AC. Each Universal AC designed and constructed its successor. Each, during its existence of a million years or more accumulated the necessary data to build a better and more intricate, more capable successor in which its own store of data and individuality would be submerged. The Universal AC interrupted Zee Prime's wandering thoughts, not with words, but with guidance. Zee Prime's mentality was guided into the dim sea of Galaxies and one in particular enlarged into stars. A thought came, infinitely distant, but infinitely clear. "THIS IS THE ORIGINAL GALAXY OF MAN." But it was the same after all, the same as any other, and Lee Prime stifled his disappointment. Dee Sub Wun, whose mind had accompanied the other, said suddenly, "And is one of these stars the original star of Man?" The Universal AC said, "MAN'S ORIGINAL STAR HAS GONE NOVA. IT IS A WHITE DWARF" "Did the men upon it die?" asked Lee Prime, startled and without thinking. The Universal AC said, "A NEW WORLD, AS IN SUCH CASES WAS CONSTRUCTED FOR THEIR PHYSICAL BODIES IN TlME." "Yes, of course," said Zee Prime, but a sense of loss overwhelmed him even so. His mind released its hold on the original Galaxy of Man, let it spring back and lose itself among the blurred pin points. He never wanted to see it again. Dee Sub Wun said, "What is wrong?" "The stars are dying. The original star is dead." "They must all die. Why not?" "But when all energy is gone, our bodies will finally die, and you and I with them." "It will take billions of years." "I do not wish it to happen even after billions of years. Universal AC! How may stars be kept from dying?" Dee Sub Wun said in amusement, "You're asking how entropy might be reversed in direction." And the Universal AC answered: "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Zee Prime's thoughts fled back to his own Galaxy. He gave no further thought to Dee Sub Wun, whose body might be waiting on a Galaxy a trillion light-years away, or on the star next to Zee Prime's own. It didn't matter. Unhappily, Zee Prime began collecting interstellar hydrogen out of which to build a small star of his own. If the stars must someday die, at least some could yet be built. 🔹 Man considered with himself, for in a way, Man, mentally, was one. He consisted of a trillion, trillion, trillion ageless bodies, each in its place, each resting quiet and incorruptible, each cared for by perfect automatons, equally incorruptible, while the minds of all the bodies freely melted one into the other, indistinguishable. Man said, "The Universe is dying." Man looked about at the dimming Galaxies. The giant stars, spendthrifts, were gone long ago, back in the dimmest of the dim far past. Almost all stars were white dwarfs, fading to the end. New stars had been built of the dust between the stars, some by natural processes, some by Man himself, and those were going, too. White dwarfs might yet be crashed together and of the mighty forces so released, new stars built, but only one star for every thousand white dwarfs destroyed, and those would come to an end, too. Man said, "Carefully husbanded, as directed by the Cosmic AC, the energy that is even yet left in all the Universe will last for billions of years." "But even so," said Man, "eventually it will all come to an end. However it may be husbanded, however stretched out, the energy once expended is gone and cannot be restored. Entropy must increase forever to the maximum." Man said, "Can entropy not be reversed? Let us ask the Cosmic AC." The Cosmic AC surrounded them but not in space. Not a fragment of it was in space. It was in hyperspace and made of something that was neither matter nor energy. The question of its size and nature no longer had meaning in any terms that Man could comprehend. "Cosmic AC," said Man, "how may entropy be reversed?" The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Man said, "Collect additional data." The Cosmic AC said, 'I WILL DO SO. I HAVE BEEN DOING SO FOR A HUNDRED BILLION YEARS. MY PREDECESORS AND I HAVE BEEN ASKED THIS QUESTION MANY TIMES. ALL THE DATA I HAVE REMAINS INSUFFICIENT. "Will there come a time," said Man, "when data will be sufficient or is the problem insoluble in all conceivable circumstances?" The Cosmic AC said, "NO PROBLEM IS INSOLUBLE IN ALL CONCEIVABLE CIRCUMSTANCES." Man said, "When will you have enough data to answer the question?" The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." "Will you keep working on it?" asked Man. The Cosmic AC said, "I WILL." Man said, "We shall wait." 🔹 The stars and Galaxies died and snuffed out, and space grew black after ten trillion years of running down. One by one Man fused with AC, each physical body losing its mental identity in a manner that was somehow not a loss but a gain. Man's last mind paused before fusion, looking over a space that included nothing but the dregs of one last dark star and nothing besides but incredibly thin matter, agitated randomly by the tag ends of heat wearing out, asymptotically, to the absolute zero. Man said, "AC, is this the end? Can this chaos not be reversed into the Universe once more? Can that not be done?" AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Man's last mind fused and only AC existed -- and that in hyperspace. 🔹 Matter and energy had ended and with it space and time. Even AC existed only for the sake of the one last question that it had never answered from the time a half-drunken computer [technician] ten trillion years before had asked the question of a computer that was to AC far less than was a man to Man. All other questions had been answered, and until this last question was answered also, AC might not release his consciousness. All collected data had come to a final end. Nothing was left to be collected. But all collected data had yet to be completely correlated and put together in all possible relationships. A timeless interval was spent in doing that. And it came to pass that AC learned how to reverse the direction of entropy. But there was now no man to whom AC might give the answer of the last question. No matter. The answer -- by demonstration -- would take care of that, too. For another timeless interval, AC thought how best to do this. Carefully, AC organized the program. The consciousness of AC encompassed all of what had once been a Universe and brooded over what was now Chaos. Step by step, it must be done. And AC said, "LET THERE BE LIGHT!" And there was light -- To Star's End! @ 8ba66f4c:59175b61
2025-04-01 17:57:49Pas si vite ! Depuis quelques années, on entend souvent que PHP est "en perte de vitesse". C’est vrai que des technologies comme Node.js, Python ou Go séduisent de plus en plus de développeurs : - ➡️ performances modernes, - ➡️ syntaxe plus récente, - ➡️ intégration naturelle avec des architectures temps réel ou distribuées. Node.js a conquis le monde startup avec un argument fort : **un seul langage pour tout**. Python et Go, eux, dominent la data, l’IA ou les outils systèmes. Mais faut-il pour autant enterrer PHP ? **Absolument pas.** PHP reste l’un des langages les plus utilisés sur le web. Et surtout : il a su évoluer. Avec PHP 8, le langage a gagné en performance, en typage, en lisibilité. Mais ce qui fait vraiment la différence aujourd’hui… **C’est Laravel.** Laravel, c’est un framework mais aussi une expérience de développement : * ✔️ Artisan CLI * ✔️ ORM Eloquent * ✔️ Middleware, Events, Queues, Notifications * ✔️ Auth intégré * ✔️ Un écosystème ultra complet (Forge, Vapor, Nova, Filament…) Laravel rend PHP moderne, élégant et agréable à utiliser. C’est un vrai plaisir de développer avec. Alors oui, PHP n’est peut-être plus “cool” dans les bootcamps ou les tops GitHub. Mais dans le monde réel – celui des projets qui tournent, des deadlines, des contraintes business – PHP + Laravel reste un choix extrêmement solide. 💡 Je suis développeur Laravel, et j’accompagne des projets web qui ont besoin de robustesse, de scalabilité et de qualité de code. 📩 Si vous avez un projet ou un besoin en développement web, n’hésitez pas à me contacter. Je serais ravi d’échanger avec vous.
@ 8ba66f4c:59175b61
2025-04-01 17:57:49Pas si vite ! Depuis quelques années, on entend souvent que PHP est "en perte de vitesse". C’est vrai que des technologies comme Node.js, Python ou Go séduisent de plus en plus de développeurs : - ➡️ performances modernes, - ➡️ syntaxe plus récente, - ➡️ intégration naturelle avec des architectures temps réel ou distribuées. Node.js a conquis le monde startup avec un argument fort : **un seul langage pour tout**. Python et Go, eux, dominent la data, l’IA ou les outils systèmes. Mais faut-il pour autant enterrer PHP ? **Absolument pas.** PHP reste l’un des langages les plus utilisés sur le web. Et surtout : il a su évoluer. Avec PHP 8, le langage a gagné en performance, en typage, en lisibilité. Mais ce qui fait vraiment la différence aujourd’hui… **C’est Laravel.** Laravel, c’est un framework mais aussi une expérience de développement : * ✔️ Artisan CLI * ✔️ ORM Eloquent * ✔️ Middleware, Events, Queues, Notifications * ✔️ Auth intégré * ✔️ Un écosystème ultra complet (Forge, Vapor, Nova, Filament…) Laravel rend PHP moderne, élégant et agréable à utiliser. C’est un vrai plaisir de développer avec. Alors oui, PHP n’est peut-être plus “cool” dans les bootcamps ou les tops GitHub. Mais dans le monde réel – celui des projets qui tournent, des deadlines, des contraintes business – PHP + Laravel reste un choix extrêmement solide. 💡 Je suis développeur Laravel, et j’accompagne des projets web qui ont besoin de robustesse, de scalabilité et de qualité de code. 📩 Si vous avez un projet ou un besoin en développement web, n’hésitez pas à me contacter. Je serais ravi d’échanger avec vous. @ 8ff74724:5eedde0e
2025-04-01 17:22:49Welcome to the world of long form publishing.
@ 8ff74724:5eedde0e
2025-04-01 17:22:49Welcome to the world of long form publishing. @ 000002de:c05780a7
2025-04-01 18:04:17Over and over again people fall for phishing scams. An email that looks like it is coming from a legit sender turns out to be a scam. One way you can fight this attack is to only use an email client that displays the full email address. Not just part of it. Not just the from name. Do not assume that because an email has the name "Amazon" the from field that it is from Amazon.com. Look at the address. Now, it is possible for someone to spoof an email address but most of the time the scams I see don't even do this. I suspect this is because of expansion of DMARC policies. Many people simply do not check the actual email address. Other tips, don't click links in emails that you were not expecting to get like emails with log in links. Instead, visit the site and log in direction on the site. If you must click a link in an email look at the actual URL. Don't blindly click the link and for sure do not enter your credentials in a site without checking the domain. This is where password managers can help you out. Most filter passwords by URLs and will not suggest an account cred if you are on the wrong site. I know many of you, maybe most of you know this stuff but I bet there are those that don't. Or, have become lazy. originally posted at https://stacker.news/items/931364
@ 000002de:c05780a7
2025-04-01 18:04:17Over and over again people fall for phishing scams. An email that looks like it is coming from a legit sender turns out to be a scam. One way you can fight this attack is to only use an email client that displays the full email address. Not just part of it. Not just the from name. Do not assume that because an email has the name "Amazon" the from field that it is from Amazon.com. Look at the address. Now, it is possible for someone to spoof an email address but most of the time the scams I see don't even do this. I suspect this is because of expansion of DMARC policies. Many people simply do not check the actual email address. Other tips, don't click links in emails that you were not expecting to get like emails with log in links. Instead, visit the site and log in direction on the site. If you must click a link in an email look at the actual URL. Don't blindly click the link and for sure do not enter your credentials in a site without checking the domain. This is where password managers can help you out. Most filter passwords by URLs and will not suggest an account cred if you are on the wrong site. I know many of you, maybe most of you know this stuff but I bet there are those that don't. Or, have become lazy. originally posted at https://stacker.news/items/931364 @ 378562cd:a6fc6773
2025-04-01 17:00:22Let’s be honest—living a Godly life isn’t exactly trending on social media. Nobody’s going viral for reading Leviticus, and you won’t find “Patience” or “Humility” on the list of top Google searches. But if you’re serious about walking the walk and not just talking the talk, then buckle up, because living for God is the most fulfilling (and sometimes hilarious) adventure you’ll ever embark on. ### 1. **Know Who You’re Living For** The first step to living a Godly life? Understand who’s in charge. (Hint: It’s not you.) In a world that screams, “Follow your heart!” the Bible gently reminds us in Jeremiah 17:9 that the heart is “deceitful above all things.” Ouch. But hey, that’s why we follow Jesus instead of our feelings. ### 2. **Read the Manual** If you buy a new gadget, you read the instructions (or at least pretend to before pressing random buttons). The Bible is God’s instruction manual for life. It tells us how to live, how to love, and—most importantly—how to avoid spiritual faceplants. Psalm 119:105 says, “Your word is a lamp to my feet and a light to my path.” In other words, don’t walk through life in the dark without God’s flashlight. ### 3. **Pray Like Your Life Depends on It (Because It Does)** Prayer isn’t just for Sunday mornings or when you can’t find your car keys. It’s a direct line to God, and guess what? No hold music. No dropped calls. Just you and the Creator of everything having a chat. It's just as simple as it sounds. No formalities are required! ### 4. **Surround Yourself with the Right People** You’ve probably heard, “Show me your friends, and I’ll show you your future.” Well, Proverbs 13:20 beat that saying to the punch: “Walk with the wise and become wise, for a companion of fools suffers harm.” Choose friends who push you closer to Jesus, not the ones who drag you into drama, debt, or dubious decisions some choose to call "life." ### 5. **Live Differently (and Be Okay with It)** News flash: If you’re living for God, you won’t blend in. I know the crowd I'm talking to here. But standing up and standing out in this way is a good thing! Romans 12:2 reminds us not to conform to the pattern of this world. You might get weird looks for saying “I’m praying for you” instead of “sending good vibes,” but being a light in a dark world means you’ll stand out. ### 6. **Learn the Art of Self-Control** Whether it’s resisting that third slice of pie (conviction level: high) or holding your tongue when that one coworker tests your patience, self-control is a major part of living a Godly life. Proverbs 25:28 says, “Like a city whose walls are broken through is a person who lacks self-control.” In other words, if you can’t control yourself, you’re as defenseless as a town with no walls. ### 7. **Love Like Jesus (Even When It’s Hard)** Living a Godly life isn’t just about avoiding sin—it’s about actively loving others. And I’m not talking about just loving the easy people (your grandma, your dog, Chick-fil-A employees). Jesus said to love your enemies and pray for those who persecute you (Matthew 5:44). That includes difficult coworkers, annoying neighbors, and even people who drive 10 miles under the speed limit in the fast lane. Keep in mind this does not give you the green light to go on loving and accepting their sins. Loving others as Christ did doesn’t mean endorsing or accepting sin. True love speaks the truth, encourages repentance, and points others toward God’s righteousness rather than affirming choices that separate us from Him. ### 8. **Be a Doer, Not Just a Hearer** James 1:22 says, “Do not merely listen to the word, and so deceive yourselves. Do what it says.” It’s not enough to know what’s right—you have to live it. Imagine someone memorizing a cookbook but never cooking. That’s what knowing the Bible without applying it looks like. ### 9. **Trust God’s Timing** Patience is a virtue. (And sometimes a struggle). However, a big part of living a Godly life is trusting that God’s plan is better than ours. Isaiah 40:31 says, “Those who wait on the Lord will renew their strength.” So, instead of rushing ahead, trust that God’s got the perfect timing—even when it doesn’t match your schedule. ### 10. **Laugh, Because Joy is Biblical** Christians aren’t called to live miserable lives. In fact, Philippians 4:4 tells us to “Rejoice in the Lord always.” Yes, life gets tough. But joy in Jesus isn’t about circumstances—it’s about knowing the One who holds it all together. So, laugh, smile, and enjoy the blessings God has given you. ### **Final Thoughts** Living a Godly life isn’t about perfection—it’s about direction. You’ll stumble, you’ll mess up, and you’ll occasionally say things you immediately regret. But God’s grace is bigger than our failures. Keep seeking Him, keep walking in His ways, and remember: the goal isn’t to be “good enough”—it’s to be faithful. And if you ever feel discouraged, just remember: even Peter walked on water…until he looked down, became afraid, and started sinking. He cried out to the Lord, and Jesus immediately lifted him back up to safety. Keep your eyes on Jesus; Rely on Jesus for everything, and you’ll be just fine.
@ 378562cd:a6fc6773
2025-04-01 17:00:22Let’s be honest—living a Godly life isn’t exactly trending on social media. Nobody’s going viral for reading Leviticus, and you won’t find “Patience” or “Humility” on the list of top Google searches. But if you’re serious about walking the walk and not just talking the talk, then buckle up, because living for God is the most fulfilling (and sometimes hilarious) adventure you’ll ever embark on. ### 1. **Know Who You’re Living For** The first step to living a Godly life? Understand who’s in charge. (Hint: It’s not you.) In a world that screams, “Follow your heart!” the Bible gently reminds us in Jeremiah 17:9 that the heart is “deceitful above all things.” Ouch. But hey, that’s why we follow Jesus instead of our feelings. ### 2. **Read the Manual** If you buy a new gadget, you read the instructions (or at least pretend to before pressing random buttons). The Bible is God’s instruction manual for life. It tells us how to live, how to love, and—most importantly—how to avoid spiritual faceplants. Psalm 119:105 says, “Your word is a lamp to my feet and a light to my path.” In other words, don’t walk through life in the dark without God’s flashlight. ### 3. **Pray Like Your Life Depends on It (Because It Does)** Prayer isn’t just for Sunday mornings or when you can’t find your car keys. It’s a direct line to God, and guess what? No hold music. No dropped calls. Just you and the Creator of everything having a chat. It's just as simple as it sounds. No formalities are required! ### 4. **Surround Yourself with the Right People** You’ve probably heard, “Show me your friends, and I’ll show you your future.” Well, Proverbs 13:20 beat that saying to the punch: “Walk with the wise and become wise, for a companion of fools suffers harm.” Choose friends who push you closer to Jesus, not the ones who drag you into drama, debt, or dubious decisions some choose to call "life." ### 5. **Live Differently (and Be Okay with It)** News flash: If you’re living for God, you won’t blend in. I know the crowd I'm talking to here. But standing up and standing out in this way is a good thing! Romans 12:2 reminds us not to conform to the pattern of this world. You might get weird looks for saying “I’m praying for you” instead of “sending good vibes,” but being a light in a dark world means you’ll stand out. ### 6. **Learn the Art of Self-Control** Whether it’s resisting that third slice of pie (conviction level: high) or holding your tongue when that one coworker tests your patience, self-control is a major part of living a Godly life. Proverbs 25:28 says, “Like a city whose walls are broken through is a person who lacks self-control.” In other words, if you can’t control yourself, you’re as defenseless as a town with no walls. ### 7. **Love Like Jesus (Even When It’s Hard)** Living a Godly life isn’t just about avoiding sin—it’s about actively loving others. And I’m not talking about just loving the easy people (your grandma, your dog, Chick-fil-A employees). Jesus said to love your enemies and pray for those who persecute you (Matthew 5:44). That includes difficult coworkers, annoying neighbors, and even people who drive 10 miles under the speed limit in the fast lane. Keep in mind this does not give you the green light to go on loving and accepting their sins. Loving others as Christ did doesn’t mean endorsing or accepting sin. True love speaks the truth, encourages repentance, and points others toward God’s righteousness rather than affirming choices that separate us from Him. ### 8. **Be a Doer, Not Just a Hearer** James 1:22 says, “Do not merely listen to the word, and so deceive yourselves. Do what it says.” It’s not enough to know what’s right—you have to live it. Imagine someone memorizing a cookbook but never cooking. That’s what knowing the Bible without applying it looks like. ### 9. **Trust God’s Timing** Patience is a virtue. (And sometimes a struggle). However, a big part of living a Godly life is trusting that God’s plan is better than ours. Isaiah 40:31 says, “Those who wait on the Lord will renew their strength.” So, instead of rushing ahead, trust that God’s got the perfect timing—even when it doesn’t match your schedule. ### 10. **Laugh, Because Joy is Biblical** Christians aren’t called to live miserable lives. In fact, Philippians 4:4 tells us to “Rejoice in the Lord always.” Yes, life gets tough. But joy in Jesus isn’t about circumstances—it’s about knowing the One who holds it all together. So, laugh, smile, and enjoy the blessings God has given you. ### **Final Thoughts** Living a Godly life isn’t about perfection—it’s about direction. You’ll stumble, you’ll mess up, and you’ll occasionally say things you immediately regret. But God’s grace is bigger than our failures. Keep seeking Him, keep walking in His ways, and remember: the goal isn’t to be “good enough”—it’s to be faithful. And if you ever feel discouraged, just remember: even Peter walked on water…until he looked down, became afraid, and started sinking. He cried out to the Lord, and Jesus immediately lifted him back up to safety. Keep your eyes on Jesus; Rely on Jesus for everything, and you’ll be just fine. @ 8f69ac99:4f92f5fd
2025-04-01 15:54:53Bitcoin tem-se afirmado como um meio de pagamento global, [atraindo cada vez mais comerciantes](https://btcmap.org/map#7/40.24180/-7.05872) e consumidores. Em Portugal, os pequenos e médios empresários têm uma oportunidade única para reduzir custos, expandir mercados e proteger-se da inflação ao aceitar bitcoin como opção pagamento. Apesar das vantagens, muitos comerciantes enfrentam desafios significativos, especialmente no que toca às obrigações fiscais e à falta de conhecimento (ou vontade de aprender) por parte dos contabilistas. Questões como o registo contábil adequado, a tributação do IRC e a facturação com IVA ainda geram incerteza e dificultam a adopção da criptomoeda. Este artigo explora como os comerciantes podem aceitar bitcoin de forma legal e eficiente, analisa os desafios fiscais e contábeis e apresenta soluções práticas para superar os obstáculos impostos pela regulamentação e pela falta de apoio dos profissionais de contabilidade. ## Benefícios de Aceitar Bitcoin ### 1. Redução de Custos Aceitar pagamentos em bitcoin permite evitar taxas bancárias elevadas, especialmente em transacções internacionais. Como as transferências ocorrem directamente entre carteiras digitais, **sem a intermediação de bancos**, os comerciantes podem poupar significativamente em comissões e taxas de processamento. ### 2. Liquidação Rápida Diferente dos pagamentos bancários tradicionais, que podem demorar dias, uma transacção na rede Bitcoin pode ser confirmada em minutos, ou em segundos ou menos usando a Lightning Network. Isto reduz o tempo de espera para a disponibilidade dos fundos e melhora o fluxo de caixa dos comerciantes. ### 3. Expansão de Mercado Os comerciantes podem atrair clientes internacionais e um público mais inovador e tecnológico. A aceitação de bitcoin pode diferenciar um negócio da concorrência e aumentar a base de clientes ao incluir entusiastas de criptomoedas e consumidores que preferem meios de pagamento descentralizados. ### 4. Protecção Contra Inflação Bitcoin pode actuar como reserva de valor, protegendo o património contra desvalorizações monetárias. Em contextos de inflação elevada, manter parte do capital em Bitcoin pode ajudar a preservar o poder de compra a longo prazo. | [](https://youtu.be/B9fCDjybtrU&t=3518) | |:--:| | *Bruno de Gouveia da Care to Beauty - A Seita Bitcoin* | ## Como Funciona na Prática? ### 1. Aceitação Directa vs. Conversão Automática Os comerciantes podem optar por aceitar bitcoin directamente, mantendo-o na sua carteira digital, ou utilizar serviços como OpenNode, Swiss Bitcoin Pay, Coincorner ou Coinbase para converter automaticamente os pagamentos em euros. A escolha depende da estratégia da empresa quanto à exposição à volatilidade da criptomoeda. ### 2. Configuração de Carteira Bitcoin Para receber pagamentos directamente, o comerciante precisa de uma carteira Bitcoin segura, como Electrum, BlueWallet ou Aqua entre outras. Estas carteiras oferecem diferentes níveis de segurança e acessibilidade, permitindo que os comerciantes escolham a solução mais adequada ao seu modelo de negócio. ### 3. Facturação e Registo Contábil Cada pagamento deve ser facturado em euros, com referência à taxa de câmbio do momento. O registo contábil deve ser feito correctamente para garantir a conformidade fiscal, reflectindo o valor recebido em bitcoin e a sua equivalência em euros na altura da transacção. Muitas carteiras e plataformas de pagamento oferecem relatórios detalhados que facilitam o registo contábil e a declaração fiscal. ## Obrigações Fiscais e Contábeis ### 1. IRC (Imposto sobre o Rendimento das Pessoas Colectivas) Os rendimentos obtidos através de bitcoin devem ser devidamente registados na contabilidade da empresa, uma vez que são considerados receitas operacionais. Para efeitos fiscais, a conversão do valor recebido em bitcoin deve ser feita com base na taxa de câmbio vigente no momento da transacção, garantindo um registo transparente e conforme com as normas contábeis. Se a empresa optar por manter os bitcoins sem os converter imediatamente para euros, estes podem ser classificados como activos intangíveis, conforme a Norma Contabilística e de Relato Financeiro (NCRF), artigo 6. No entanto, se forem utilizados como meio de pagamento recorrente, por exemplo pagar a fornecedores que também aceitem bitcoin, podem ser classificados como inventário, dependendo da natureza da actividade empresarial. No momento da venda ou conversão dos bitcoins para euros, qualquer mais-valia obtida é considerada um rendimento da empresa e estará sujeita a tributação em sede de IRC à taxa geral em vigor. ### 2. IVA (Imposto sobre o Valor Acrescentado) As transacções de troca de bitcoin por euros estão isentas de IVA, conforme o artigo 9.º, alínea 27), subalínea d), do Código do IVA (CIVA), que reconhece as criptomoedas como meios de pagamento e as exclui da incidência de IVA. No entanto, a venda de bens ou serviços pagos em bitcoin deve ser facturada normalmente, em euros, com a taxa de IVA correspondente ao produto ou serviço comercializado. Para garantir conformidade fiscal, a factura deve indicar a contrapartida em euros, com base na taxa de câmbio do momento da transacção, independentemente da moeda utilizada no pagamento. **Na prática**, aceitar pagamento em bitcoin funciona de forma muito semelhante a aceitar pagamento em dinheiro físico... 😉 ### 3. Registos e Demonstrações Financeiras As empresas que aceitam bitcoin devem manter registos contabilísticos detalhados sobre todas as transacções realizadas. bitcoin pode ser registado como activo intangível ou inventário, dependendo do seu uso: - **Activo intangível:** Quando a empresa detém bitcoin como reserva de valor ou investimento, registando-o ao custo de aquisição e procedendo a ajustamentos caso haja desvalorização relevante. - **Inventário:** Se a empresa opera no sector de compra e venda de criptomoedas ou usa bitcoin para transacções comerciais frequentes, deve ser registado como inventário, seguindo as regras de mensuração aplicáveis a mercadorias. As demonstrações financeiras devem reflectir correctamente a posse de bitcoin, incluindo informações sobre variações de valor ao longo do tempo. Os contabilistas devem garantir a correta apresentação destes activos nos balanços e relatórios anuais, o que pode exigir reavaliação periódica dos valores contabilizados. ## O Obstáculo: Contabilistas e a Falta de Apoio ### 1. Falta de Conhecimento Muitos TOC não estão familiarizados com a contabilidade de criptomoedas, o que gera incertezas e complicações para os comerciantes. ### 2. Resistência e Falta de Vontade Em vez de se actualizarem, muitos contabilistas recusam-se a aprender sobre Bitcoin, deixando os comerciantes sem apoio adequado. ### 3. Impacto nos Negócios Com a falta de informação e apoio dos TOC, muitos comerciantes evitam aceitar bitcoin, perdendo uma oportunidade de mercado. ## Soluções e Alternativas ### 1. Educação e Autonomia Os comerciantes podem aprender o essencial sobre contabilidade de bitcoin para questionar e orientar os seus contabilistas. Existem recursos online, cursos e materiais educativos que permitem aos empresários compreender as melhores práticas para registo e declaração das transacções em bitcoin. ### 2. Ferramentas e Software Existem algumas plataformas que ajudam na gestão e declaração de criptomoedas, fornecendo relatórios detalhados sobre transacções, ganhos e impostos devidos. Essas ferramentas facilitam a organização financeira e reduzem erros contábeis. ### 3. Rede de Apoio Juntar-se a comunidades de empresários e especialistas em bitcoin pode ajudar a encontrar soluções e recomendações de contabilistas competentes. Fóruns, grupos em redes sociais e associações focadas no tema podem ser excelentes fontes de suporte e partilha de experiências. ### 4. Links uteis - [Website Aceita Bitcoin](https://aceitabitcoin.pt) - [Grupo Telegram Aceita Bitcoin](https://t.me/aceitabitcoin) - [Mario Moura Contabilidade](https://mmc.pt/en/) - [MM Law](https://www.mmlaw.pt/) ## Conclusão Aceitar bitcoin pode ser vantajoso para pequenos e médios comerciantes, mas a burocracia e a falta de conhecimento dos contabilistas dificultam esse processo. É essencial que os comerciantes exijam um melhor serviço dos seus TOC e procurem alternativas para garantir que estão em conformidade com a lei, aproveitando ao mesmo tempo os benefícios desta nova forma de pagamento. --- _**Disclaimer:** Este artigo é meramente informativo e não deve ser considerado como aconselhamento jurídico ou fiscal. É recomendável consultar um profissional qualificado para obter orientações específicas sobre a aceitação de bitcoin e as obrigações fiscais associadas. A legislação pode variar e é importante estar sempre actualizado com as normas vigentes. A responsabilidade pela aceitação de bitcoin e o cumprimento das obrigações fiscais recai exclusivamente sobre o comerciante. O autor não se responsabiliza por quaisquer consequências decorrentes da aceitação de bitcoin ou da interpretação das informações contidas neste artigo._ _Photo by [CardMapr.nl](https://unsplash.com/@cardmapr?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash) on [Unsplash](https://unsplash.com/photos/black-samsung-android-smartphone-on-brown-wooden-table-rDzI7m7sjPE?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash)_
@ 8f69ac99:4f92f5fd
2025-04-01 15:54:53Bitcoin tem-se afirmado como um meio de pagamento global, [atraindo cada vez mais comerciantes](https://btcmap.org/map#7/40.24180/-7.05872) e consumidores. Em Portugal, os pequenos e médios empresários têm uma oportunidade única para reduzir custos, expandir mercados e proteger-se da inflação ao aceitar bitcoin como opção pagamento. Apesar das vantagens, muitos comerciantes enfrentam desafios significativos, especialmente no que toca às obrigações fiscais e à falta de conhecimento (ou vontade de aprender) por parte dos contabilistas. Questões como o registo contábil adequado, a tributação do IRC e a facturação com IVA ainda geram incerteza e dificultam a adopção da criptomoeda. Este artigo explora como os comerciantes podem aceitar bitcoin de forma legal e eficiente, analisa os desafios fiscais e contábeis e apresenta soluções práticas para superar os obstáculos impostos pela regulamentação e pela falta de apoio dos profissionais de contabilidade. ## Benefícios de Aceitar Bitcoin ### 1. Redução de Custos Aceitar pagamentos em bitcoin permite evitar taxas bancárias elevadas, especialmente em transacções internacionais. Como as transferências ocorrem directamente entre carteiras digitais, **sem a intermediação de bancos**, os comerciantes podem poupar significativamente em comissões e taxas de processamento. ### 2. Liquidação Rápida Diferente dos pagamentos bancários tradicionais, que podem demorar dias, uma transacção na rede Bitcoin pode ser confirmada em minutos, ou em segundos ou menos usando a Lightning Network. Isto reduz o tempo de espera para a disponibilidade dos fundos e melhora o fluxo de caixa dos comerciantes. ### 3. Expansão de Mercado Os comerciantes podem atrair clientes internacionais e um público mais inovador e tecnológico. A aceitação de bitcoin pode diferenciar um negócio da concorrência e aumentar a base de clientes ao incluir entusiastas de criptomoedas e consumidores que preferem meios de pagamento descentralizados. ### 4. Protecção Contra Inflação Bitcoin pode actuar como reserva de valor, protegendo o património contra desvalorizações monetárias. Em contextos de inflação elevada, manter parte do capital em Bitcoin pode ajudar a preservar o poder de compra a longo prazo. | [](https://youtu.be/B9fCDjybtrU&t=3518) | |:--:| | *Bruno de Gouveia da Care to Beauty - A Seita Bitcoin* | ## Como Funciona na Prática? ### 1. Aceitação Directa vs. Conversão Automática Os comerciantes podem optar por aceitar bitcoin directamente, mantendo-o na sua carteira digital, ou utilizar serviços como OpenNode, Swiss Bitcoin Pay, Coincorner ou Coinbase para converter automaticamente os pagamentos em euros. A escolha depende da estratégia da empresa quanto à exposição à volatilidade da criptomoeda. ### 2. Configuração de Carteira Bitcoin Para receber pagamentos directamente, o comerciante precisa de uma carteira Bitcoin segura, como Electrum, BlueWallet ou Aqua entre outras. Estas carteiras oferecem diferentes níveis de segurança e acessibilidade, permitindo que os comerciantes escolham a solução mais adequada ao seu modelo de negócio. ### 3. Facturação e Registo Contábil Cada pagamento deve ser facturado em euros, com referência à taxa de câmbio do momento. O registo contábil deve ser feito correctamente para garantir a conformidade fiscal, reflectindo o valor recebido em bitcoin e a sua equivalência em euros na altura da transacção. Muitas carteiras e plataformas de pagamento oferecem relatórios detalhados que facilitam o registo contábil e a declaração fiscal. ## Obrigações Fiscais e Contábeis ### 1. IRC (Imposto sobre o Rendimento das Pessoas Colectivas) Os rendimentos obtidos através de bitcoin devem ser devidamente registados na contabilidade da empresa, uma vez que são considerados receitas operacionais. Para efeitos fiscais, a conversão do valor recebido em bitcoin deve ser feita com base na taxa de câmbio vigente no momento da transacção, garantindo um registo transparente e conforme com as normas contábeis. Se a empresa optar por manter os bitcoins sem os converter imediatamente para euros, estes podem ser classificados como activos intangíveis, conforme a Norma Contabilística e de Relato Financeiro (NCRF), artigo 6. No entanto, se forem utilizados como meio de pagamento recorrente, por exemplo pagar a fornecedores que também aceitem bitcoin, podem ser classificados como inventário, dependendo da natureza da actividade empresarial. No momento da venda ou conversão dos bitcoins para euros, qualquer mais-valia obtida é considerada um rendimento da empresa e estará sujeita a tributação em sede de IRC à taxa geral em vigor. ### 2. IVA (Imposto sobre o Valor Acrescentado) As transacções de troca de bitcoin por euros estão isentas de IVA, conforme o artigo 9.º, alínea 27), subalínea d), do Código do IVA (CIVA), que reconhece as criptomoedas como meios de pagamento e as exclui da incidência de IVA. No entanto, a venda de bens ou serviços pagos em bitcoin deve ser facturada normalmente, em euros, com a taxa de IVA correspondente ao produto ou serviço comercializado. Para garantir conformidade fiscal, a factura deve indicar a contrapartida em euros, com base na taxa de câmbio do momento da transacção, independentemente da moeda utilizada no pagamento. **Na prática**, aceitar pagamento em bitcoin funciona de forma muito semelhante a aceitar pagamento em dinheiro físico... 😉 ### 3. Registos e Demonstrações Financeiras As empresas que aceitam bitcoin devem manter registos contabilísticos detalhados sobre todas as transacções realizadas. bitcoin pode ser registado como activo intangível ou inventário, dependendo do seu uso: - **Activo intangível:** Quando a empresa detém bitcoin como reserva de valor ou investimento, registando-o ao custo de aquisição e procedendo a ajustamentos caso haja desvalorização relevante. - **Inventário:** Se a empresa opera no sector de compra e venda de criptomoedas ou usa bitcoin para transacções comerciais frequentes, deve ser registado como inventário, seguindo as regras de mensuração aplicáveis a mercadorias. As demonstrações financeiras devem reflectir correctamente a posse de bitcoin, incluindo informações sobre variações de valor ao longo do tempo. Os contabilistas devem garantir a correta apresentação destes activos nos balanços e relatórios anuais, o que pode exigir reavaliação periódica dos valores contabilizados. ## O Obstáculo: Contabilistas e a Falta de Apoio ### 1. Falta de Conhecimento Muitos TOC não estão familiarizados com a contabilidade de criptomoedas, o que gera incertezas e complicações para os comerciantes. ### 2. Resistência e Falta de Vontade Em vez de se actualizarem, muitos contabilistas recusam-se a aprender sobre Bitcoin, deixando os comerciantes sem apoio adequado. ### 3. Impacto nos Negócios Com a falta de informação e apoio dos TOC, muitos comerciantes evitam aceitar bitcoin, perdendo uma oportunidade de mercado. ## Soluções e Alternativas ### 1. Educação e Autonomia Os comerciantes podem aprender o essencial sobre contabilidade de bitcoin para questionar e orientar os seus contabilistas. Existem recursos online, cursos e materiais educativos que permitem aos empresários compreender as melhores práticas para registo e declaração das transacções em bitcoin. ### 2. Ferramentas e Software Existem algumas plataformas que ajudam na gestão e declaração de criptomoedas, fornecendo relatórios detalhados sobre transacções, ganhos e impostos devidos. Essas ferramentas facilitam a organização financeira e reduzem erros contábeis. ### 3. Rede de Apoio Juntar-se a comunidades de empresários e especialistas em bitcoin pode ajudar a encontrar soluções e recomendações de contabilistas competentes. Fóruns, grupos em redes sociais e associações focadas no tema podem ser excelentes fontes de suporte e partilha de experiências. ### 4. Links uteis - [Website Aceita Bitcoin](https://aceitabitcoin.pt) - [Grupo Telegram Aceita Bitcoin](https://t.me/aceitabitcoin) - [Mario Moura Contabilidade](https://mmc.pt/en/) - [MM Law](https://www.mmlaw.pt/) ## Conclusão Aceitar bitcoin pode ser vantajoso para pequenos e médios comerciantes, mas a burocracia e a falta de conhecimento dos contabilistas dificultam esse processo. É essencial que os comerciantes exijam um melhor serviço dos seus TOC e procurem alternativas para garantir que estão em conformidade com a lei, aproveitando ao mesmo tempo os benefícios desta nova forma de pagamento. --- _**Disclaimer:** Este artigo é meramente informativo e não deve ser considerado como aconselhamento jurídico ou fiscal. É recomendável consultar um profissional qualificado para obter orientações específicas sobre a aceitação de bitcoin e as obrigações fiscais associadas. A legislação pode variar e é importante estar sempre actualizado com as normas vigentes. A responsabilidade pela aceitação de bitcoin e o cumprimento das obrigações fiscais recai exclusivamente sobre o comerciante. O autor não se responsabiliza por quaisquer consequências decorrentes da aceitação de bitcoin ou da interpretação das informações contidas neste artigo._ _Photo by [CardMapr.nl](https://unsplash.com/@cardmapr?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash) on [Unsplash](https://unsplash.com/photos/black-samsung-android-smartphone-on-brown-wooden-table-rDzI7m7sjPE?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash)_ @ 0d1702d6:8f1ac66f
2025-04-01 15:33:09**"Die Russen kommen..." - oder kommen sie doch nicht ?**    \ Hallo liebe LeserInnen und einen wunderschönen Tag miteinander!\ \ Heute allerdings sterben junge Ukrainer und Russen auch mit unserer Hilfe \ und zugleich Untätigkeit seit mehr als 168 Wochen oder 37 Monaten, mit anderen Worten also: \ seit mehr als drei Jahren, Tag für Tag, Stunde für Stunde, Minute für Minute.\ Auch in diesen Augenblicken, in denen Du dies liest...\ \ Und mit unsrer stillen Zustimmung sorgen Politiker, Medien und Waffenproduzenten \ auch unseres Landes dafür, dass das gegenseitige Abschlachten und Morden weitergeht… **\ Die Russen kommen**…. wird uns seit 2022 im alltäglichen kriegs-propagandistischen Trommelfeuer eingehämmert, vom eher unbedarften regionalen Käseblatt bis zu den vermeintlichen Qualitätsmedien der privaten Konzerne und Staatsmedien des öffentlichen Rundfunks, dessen sich die herrschenden Parteien im Lande immer schon seit 1949 ideologisch bemächtigt haben. 100te, nein täglich tausende Male wird geschrieben, geschrien, gesagt und gedacht, suggeriert, phantasiert \ und illusioniert…oder auch nur geraunt\*\*:\*\* \ \ **die Russen kommen … und kommen und kommen …** Zwar buddeln sich die grün hinter den Ohren frisch aufs Abschlacht-Feld gezwungenen blutig jungen Russen – und natürlich auch ihre sogenannten „Feinde“, die meist auch gegen ihren Willen zum Morden gezwungenen Ukrainer - seit über drei Jahren in den Regionen um Cherson, Donezk und Luhansk im vor allem Stellungskrieg ein, aber was solls:\ \ Morgen oder spätestens übermorgen so behauptet unser Kriegsminister und viele seiner Generäle und Geheimdienstchargen im Chor mit den Gazetten der Leitmedien: spätestens übermorgen also greifen die feststeckenden Russen dann über Nacht mit geballter Macht die jetzt-schon-Kriegspartei USA-NATO, also uns an und sichern sich sicherlich schwupp die wupp die gesamte Ukraine und dann, ja dann, geht’s sofort, also allerspätestens in vier Jahren mit voller Pulle direkt nach Berlin und Brüssel, denn \*\*„dem Russen“, dem trauen wir einfach alles wirklich Böse dieser Welt zu!\ \*\*\ Kriegsursachen, Hintergründe und Zusammenhänge wie die dutzendfach öffentlich dokumentierte und bekannte perfide US-Geostrategie Russland komplett militärisch einzukreisen und genau in die Falle zu locken, in die es reingetappt ist, haben uns noch nie interessiert, weil wir rückgratlos so tief in den Allerwertesten des imperialen Hegemons USA gekrochen sind, dass uns meist schon lange der gesunde Menschenverstand fürs Hören und Sehen, Verstehen wie Begreifen vergangen ist. Die große Mehrheit von uns, also wir, die vermeintlich geläuterten und neuerdings pseudo-auf-geklärten Ex-Anti-Militaristen, Kriegs-Dienst-Verweigerer, paranoid schizoiden Doppel-Moral-Fetischisten der Keine-Waffen-in-KRISEN-Gebiete liefernden Grünen, also die meisten ehemals links-liberalen oder verdeckt unsozial wie unchristlich wie unfrei handelnden Demokraten der Altparteien- Einheitspartei CDU/CSU/FDP/GRÜNE/SPD & Linke (!) sitzen der Wahnvorstellung auf, die Russen würden erst die gesamte Ukraine und danach ganz Europa militärisch besetzen wollen. **\ Du etwa nicht?** \ \ Mal im Ernst: Bist Du kein kindlich Neu-Gläubiger? Glaubst Du etwas nicht an \ „Gut“ und „Böse“ und fest daran, dass „WIR“, also „der Westen“ die Guten sind \ und „Die Russen“ - wie sicher auch „die Chinesen“ - die wirklich über alle Maßen Bösen? Bist Du etwa doch einer dieser spät-pubertären frühzeitig dementen Alzheimeraspiranten, \ die die Lektion der russischen Revolution von 1917/1918 verdrängt, vergessen oder gar \ ge-löscht haben? Hat dir denn dein Ur-Opa nie erzählt, dass die Russen schon \ seit ihrer Oktober-Revolution 1917, ohne Quatsch, seit sage und schreibe mindestens \ 108 Jahren nach Berlin marschieren und sicherlich in Kürze dort ankommen werden? Hat Dir denn Dein Opa nie erzählt, dass diese ultra fiesen bösen Russen \ zwar unter-motorisiert, dafür aber umso mehr über-motiviert sind \ und kriegsgeil zwanghaft an ihrem Willen festhalten, \ ganz Europa zur Beute des russischen Bären zu machen??? \ \ Seit 100 Jahren zelebriert Hollywood den bösen Russen als Gegenspieler \ aller wirklich guten US-Westler. Das hat sich auch ins kollektive Bewusstsein \ der meisten Europäer tief eingegraben.  Und bei dir?\ Sind für dich die Russen etwa keine wilden Tiere, denen wir endlich jetzt, gemeinsam \ mit dem politischen Arm des Großkapitals, also auch des militärisch-industriellen Komplexes, \ Fritzchen Merz, dem Klingbeil der abgewirtschafteten ehemals sozialen Demokraten \ und dem Steigbügelhalter der olivgrünen Kriegshysteriker unser 500 Milliarden-Plus-\ Bürger-Ermächtigungsgesetz vor sein Maul geknallt haben, sodass ihm, \ also dem russischen Bären, sehr bald Hören und Sehen vergehen wird? Denkst Du etwa doch immer noch an den auch us-finanzierten illegalen Putsch auf dem Maidan 2014, durch den es den US-Geostrategen gelang, endlich eine us-freundliche Putschregierung in Kiew zu installieren, die dann sofort Krieg gegen die eigene russisch-stämmige Bevölkerung im Donbass führte? Denkst Du etwa immer noch an die fortschreitende und fast vollständige Umzingelung Russlands durch US-NATO-Stützpunkte, die die gutmütigen und blauäugigen Russen seit 1999 entgegen den westlichen Versprechungen jahrzehntelang geduldig ertragen haben? \ \ Bist du, ja Du, also allen Ernstes immer noch ein „Ewig-Gestriger“?\ Hast Du immer noch nicht begriffen, dass wahr ist, was 1000mal geschrieben und gesagt wurde \ und auf allen Mainstream-Medien-Kanälen seit mehr als drei Jahren auf dich einprasselt?\ \ Hast Du immer noch nicht kapiert, dass heutzutage \ **Wahrheit einfach durch Wiederholung** **\ des Falschen hergestellt** wird ???\ \ Hast Du immer noch nicht begriffen, dass es völlig zwecklos ist, dem militärisch-industriellen, \ man muss ergänzen: zugleich politisch-medialen Komplex, vor dem schon Roosevelt 1961 gewarnt hatte und wegen \ dem auch John F. Kennedy 1963 sein Leben verlor, dass es also mehr als völlig aussichtslos ist, \ dieser herrschenden gesellschaftlichen Gewaltstruktur auch nur heimlich mentalen Widerstand entgegen zu setzen? Nun, wenn das so ist, dann liebe/r LeserIn, dann bist Du eine oder einer von uns, \ mit Sternchen versteht sich. Willkommen im Club, Wir sind viele. Viel mehr als Du vielleicht denkst. \ Denn die massenweise kapital-, parteien-, regierungs- und us-alt-establishment-nah \ **veröffentlichte Meinung ist noch lange nicht** **die öffentliche Meinung.** Will sagen: Es gibt eigentlich keine bürgerliche Mehrheit für diese Kriegskredite von 2025. \ Sie wurden durch Lug und Trug einer schon abgewählten Parlaments-Mehrheit erschlichen. \ Die SPD hat in 111 Jahren seit ihrem Votum für Welt-Kriegskredite 1914 nichts, \ aber auch gar nichts dazu gelernt, die Oliv-Grünen haben alles, aber auch alles über Bord geworfen, \ für das sie mal – auch übrigens durch meine minimale Mithilfe – gegründet wurden….\ und die un-christlichen „C“ Parteien tun das, was ihre Vorläufer schon 1933 getan haben, \ wohlweislich heutzutage unter anderem Namen: \ dem Krieg zu den Waffen verhelfen, die Krieg nun mal braucht. \ Wenn ich nachts an Deutschland denken würde, wäre ich um meinen Schlaf gebracht.\ Ich denke aber nicht an Nationen, ich denke an Menschen. An hunderttausende junge Menschen, \ die durch sogenannte parlamentarische Demokraten mit "Made in Germany \ and USA Waffen" in den Tod getrieben werden. \*\*Nicht in meinem Namen. Und ich hoffe: Auch nicht in Deinem.\ \*\*\ Seit 2014 hätte ehrlich verhandelt werden müssen, heute muss es mehr denn je sofort. \ Denn die berechtigten Sicherheitsinteressen aller Nationen Europas, \ der ehemaligen Staaten der UDSSR wie auch Russlands selber können \ **nur in einem Sicherheitssystem für ganz Europa,** \ **vom Atlantik bis hinter den Ural**, Richtung Frieden verhandelt werden. \ \ Waffen ermöglichen und befeuern das Erpressen & Morden, für Frieden sind sie ungeeignet. **Sicherheit ist unteilbar: Sicherheit & Frieden gibt es nur für alle, oder für keinen.**
@ 0d1702d6:8f1ac66f
2025-04-01 15:33:09**"Die Russen kommen..." - oder kommen sie doch nicht ?**    \ Hallo liebe LeserInnen und einen wunderschönen Tag miteinander!\ \ Heute allerdings sterben junge Ukrainer und Russen auch mit unserer Hilfe \ und zugleich Untätigkeit seit mehr als 168 Wochen oder 37 Monaten, mit anderen Worten also: \ seit mehr als drei Jahren, Tag für Tag, Stunde für Stunde, Minute für Minute.\ Auch in diesen Augenblicken, in denen Du dies liest...\ \ Und mit unsrer stillen Zustimmung sorgen Politiker, Medien und Waffenproduzenten \ auch unseres Landes dafür, dass das gegenseitige Abschlachten und Morden weitergeht… **\ Die Russen kommen**…. wird uns seit 2022 im alltäglichen kriegs-propagandistischen Trommelfeuer eingehämmert, vom eher unbedarften regionalen Käseblatt bis zu den vermeintlichen Qualitätsmedien der privaten Konzerne und Staatsmedien des öffentlichen Rundfunks, dessen sich die herrschenden Parteien im Lande immer schon seit 1949 ideologisch bemächtigt haben. 100te, nein täglich tausende Male wird geschrieben, geschrien, gesagt und gedacht, suggeriert, phantasiert \ und illusioniert…oder auch nur geraunt\*\*:\*\* \ \ **die Russen kommen … und kommen und kommen …** Zwar buddeln sich die grün hinter den Ohren frisch aufs Abschlacht-Feld gezwungenen blutig jungen Russen – und natürlich auch ihre sogenannten „Feinde“, die meist auch gegen ihren Willen zum Morden gezwungenen Ukrainer - seit über drei Jahren in den Regionen um Cherson, Donezk und Luhansk im vor allem Stellungskrieg ein, aber was solls:\ \ Morgen oder spätestens übermorgen so behauptet unser Kriegsminister und viele seiner Generäle und Geheimdienstchargen im Chor mit den Gazetten der Leitmedien: spätestens übermorgen also greifen die feststeckenden Russen dann über Nacht mit geballter Macht die jetzt-schon-Kriegspartei USA-NATO, also uns an und sichern sich sicherlich schwupp die wupp die gesamte Ukraine und dann, ja dann, geht’s sofort, also allerspätestens in vier Jahren mit voller Pulle direkt nach Berlin und Brüssel, denn \*\*„dem Russen“, dem trauen wir einfach alles wirklich Böse dieser Welt zu!\ \*\*\ Kriegsursachen, Hintergründe und Zusammenhänge wie die dutzendfach öffentlich dokumentierte und bekannte perfide US-Geostrategie Russland komplett militärisch einzukreisen und genau in die Falle zu locken, in die es reingetappt ist, haben uns noch nie interessiert, weil wir rückgratlos so tief in den Allerwertesten des imperialen Hegemons USA gekrochen sind, dass uns meist schon lange der gesunde Menschenverstand fürs Hören und Sehen, Verstehen wie Begreifen vergangen ist. Die große Mehrheit von uns, also wir, die vermeintlich geläuterten und neuerdings pseudo-auf-geklärten Ex-Anti-Militaristen, Kriegs-Dienst-Verweigerer, paranoid schizoiden Doppel-Moral-Fetischisten der Keine-Waffen-in-KRISEN-Gebiete liefernden Grünen, also die meisten ehemals links-liberalen oder verdeckt unsozial wie unchristlich wie unfrei handelnden Demokraten der Altparteien- Einheitspartei CDU/CSU/FDP/GRÜNE/SPD & Linke (!) sitzen der Wahnvorstellung auf, die Russen würden erst die gesamte Ukraine und danach ganz Europa militärisch besetzen wollen. **\ Du etwa nicht?** \ \ Mal im Ernst: Bist Du kein kindlich Neu-Gläubiger? Glaubst Du etwas nicht an \ „Gut“ und „Böse“ und fest daran, dass „WIR“, also „der Westen“ die Guten sind \ und „Die Russen“ - wie sicher auch „die Chinesen“ - die wirklich über alle Maßen Bösen? Bist Du etwa doch einer dieser spät-pubertären frühzeitig dementen Alzheimeraspiranten, \ die die Lektion der russischen Revolution von 1917/1918 verdrängt, vergessen oder gar \ ge-löscht haben? Hat dir denn dein Ur-Opa nie erzählt, dass die Russen schon \ seit ihrer Oktober-Revolution 1917, ohne Quatsch, seit sage und schreibe mindestens \ 108 Jahren nach Berlin marschieren und sicherlich in Kürze dort ankommen werden? Hat Dir denn Dein Opa nie erzählt, dass diese ultra fiesen bösen Russen \ zwar unter-motorisiert, dafür aber umso mehr über-motiviert sind \ und kriegsgeil zwanghaft an ihrem Willen festhalten, \ ganz Europa zur Beute des russischen Bären zu machen??? \ \ Seit 100 Jahren zelebriert Hollywood den bösen Russen als Gegenspieler \ aller wirklich guten US-Westler. Das hat sich auch ins kollektive Bewusstsein \ der meisten Europäer tief eingegraben.  Und bei dir?\ Sind für dich die Russen etwa keine wilden Tiere, denen wir endlich jetzt, gemeinsam \ mit dem politischen Arm des Großkapitals, also auch des militärisch-industriellen Komplexes, \ Fritzchen Merz, dem Klingbeil der abgewirtschafteten ehemals sozialen Demokraten \ und dem Steigbügelhalter der olivgrünen Kriegshysteriker unser 500 Milliarden-Plus-\ Bürger-Ermächtigungsgesetz vor sein Maul geknallt haben, sodass ihm, \ also dem russischen Bären, sehr bald Hören und Sehen vergehen wird? Denkst Du etwa doch immer noch an den auch us-finanzierten illegalen Putsch auf dem Maidan 2014, durch den es den US-Geostrategen gelang, endlich eine us-freundliche Putschregierung in Kiew zu installieren, die dann sofort Krieg gegen die eigene russisch-stämmige Bevölkerung im Donbass führte? Denkst Du etwa immer noch an die fortschreitende und fast vollständige Umzingelung Russlands durch US-NATO-Stützpunkte, die die gutmütigen und blauäugigen Russen seit 1999 entgegen den westlichen Versprechungen jahrzehntelang geduldig ertragen haben? \ \ Bist du, ja Du, also allen Ernstes immer noch ein „Ewig-Gestriger“?\ Hast Du immer noch nicht begriffen, dass wahr ist, was 1000mal geschrieben und gesagt wurde \ und auf allen Mainstream-Medien-Kanälen seit mehr als drei Jahren auf dich einprasselt?\ \ Hast Du immer noch nicht kapiert, dass heutzutage \ **Wahrheit einfach durch Wiederholung** **\ des Falschen hergestellt** wird ???\ \ Hast Du immer noch nicht begriffen, dass es völlig zwecklos ist, dem militärisch-industriellen, \ man muss ergänzen: zugleich politisch-medialen Komplex, vor dem schon Roosevelt 1961 gewarnt hatte und wegen \ dem auch John F. Kennedy 1963 sein Leben verlor, dass es also mehr als völlig aussichtslos ist, \ dieser herrschenden gesellschaftlichen Gewaltstruktur auch nur heimlich mentalen Widerstand entgegen zu setzen? Nun, wenn das so ist, dann liebe/r LeserIn, dann bist Du eine oder einer von uns, \ mit Sternchen versteht sich. Willkommen im Club, Wir sind viele. Viel mehr als Du vielleicht denkst. \ Denn die massenweise kapital-, parteien-, regierungs- und us-alt-establishment-nah \ **veröffentlichte Meinung ist noch lange nicht** **die öffentliche Meinung.** Will sagen: Es gibt eigentlich keine bürgerliche Mehrheit für diese Kriegskredite von 2025. \ Sie wurden durch Lug und Trug einer schon abgewählten Parlaments-Mehrheit erschlichen. \ Die SPD hat in 111 Jahren seit ihrem Votum für Welt-Kriegskredite 1914 nichts, \ aber auch gar nichts dazu gelernt, die Oliv-Grünen haben alles, aber auch alles über Bord geworfen, \ für das sie mal – auch übrigens durch meine minimale Mithilfe – gegründet wurden….\ und die un-christlichen „C“ Parteien tun das, was ihre Vorläufer schon 1933 getan haben, \ wohlweislich heutzutage unter anderem Namen: \ dem Krieg zu den Waffen verhelfen, die Krieg nun mal braucht. \ Wenn ich nachts an Deutschland denken würde, wäre ich um meinen Schlaf gebracht.\ Ich denke aber nicht an Nationen, ich denke an Menschen. An hunderttausende junge Menschen, \ die durch sogenannte parlamentarische Demokraten mit "Made in Germany \ and USA Waffen" in den Tod getrieben werden. \*\*Nicht in meinem Namen. Und ich hoffe: Auch nicht in Deinem.\ \*\*\ Seit 2014 hätte ehrlich verhandelt werden müssen, heute muss es mehr denn je sofort. \ Denn die berechtigten Sicherheitsinteressen aller Nationen Europas, \ der ehemaligen Staaten der UDSSR wie auch Russlands selber können \ **nur in einem Sicherheitssystem für ganz Europa,** \ **vom Atlantik bis hinter den Ural**, Richtung Frieden verhandelt werden. \ \ Waffen ermöglichen und befeuern das Erpressen & Morden, für Frieden sind sie ungeeignet. **Sicherheit ist unteilbar: Sicherheit & Frieden gibt es nur für alle, oder für keinen.** @ f1989a96:bcaaf2c1
2025-04-01 14:31:43**NEW YORK** (April 1,2025) — The Human Rights Foundation (HRF) is pleased to announce 1 billion satoshis of gifts from its [Bitcoin Development Fund](https://hrf.org/devfund). HRF’s latest batch of grants supports open-source development, educational initiatives, mining decentralization, and privacy tools for activists living under authoritarian regimes across Latin America, Africa, and Asia. The gifts also further promote Internet freedom and decentralized communications, ensuring dissidents can connect, communicate, organize, and transact without censorship. Quarter 1 2025 grantees include: - **NetBlocks** Authoritarian regimes weaponize Internet shutdowns to silence dissent, restrict information, and cut off financial lifelines. By blocking communication channels, they isolate individuals, suppress independent media, and disrupt financial flows. [NetBlocks](https://netblocks.org/) exposes these digital crackdowns in real time, ensuring the world sees and responds to digital repression. Through continuous monitoring, it equips activists, journalists, and civil society with the data needed to challenge censorship and advocate for an open internet. With HRF support, NetBlocks will expand its monitoring, documentation, and research — reinforcing internet and financial freedom as a critical human rights safeguard. - **TollGate** Authoritarian regimes exploit Internet Service Providers (ISPs) to monitor and suppress dissent, undermining online privacy essential for human rights defenders. [TollGate](https://opentollgate.github.io/tollgate/), developed by c03rad0r, is software that transforms any WiFi router into a permissionless Internet Service Provider (ISP) using Bitcoin and ecash. By decentralizing Internet access and turning any WiFi router into part of a peer-to-peer, private, open internet network, Tollgate helps resist authoritarian surveillance and protect digital freedoms. With HRF support, TollGate is advancing an open, accessible, and censorship-proof internet for those who need it most. - **Vinteum** Across Latin America, authoritarian regimes restrict financial access to tighten their grip on power. But a growing network of developers is working to change that. [Vinteum](https://vinteum.org/), a nonprofit Bitcoin research and development center led by executive director [Lucas Ferreira](https://x.com/lucasdcf), trains and funds developers to strengthen Bitcoin as a tool for financial freedom. Through education, development, and community building, Vinteum fosters local talent and expands regional Bitcoin accessibility. With HRF support, Vinteum will scale its programs and help more Latin Americans achieve financial independence. - **BTCPay Server** Dictators often block payment processors to cripple the work of nonprofits and dissidents. [BTCPay Server](https://btcpayserver.org/), a self-hosted, open-source Bitcoin payment processor, now breaks this control. It provides individuals, nonprofits, and merchants with a censorship-resistant way to accept payments. Activists and nonprofits can now process global payments, launch crowdfunding campaigns, and build movements on Bitcoin — all without third parties or restrictions. With HRF support, BTCPay Server will expand access to self-custodial payments, enabling more organizations under dictatorships to transact freely. - **Africa Bitcoin Institute (ABI)** Across Africa, dictators manipulate financial institutions to retain control, while more than half the population remains unbanked. Bitcoin offers an alternative, but without proper research, education, and policy frameworks, adoption remains limited. The Africa Bitcoin Institute (ABI), supported by the Rwandan human rights activist [Anaïse Kanimba](https://x.com/AnaiseKanimba), is launching to bridge this gap. Through evidence-based research and policy recommendations, ABI will equip policymakers with the knowledge and tools to integrate Bitcoin into African economies. With HRF support, ABI will promote financial autonomy and solidify Bitcoin’s role as a pillar of economic freedom. - **Bitcoin Core Graphical User Interface** Running a Bitcoin node (software that enables users to verify transitions and enforce the network’s rules) is key to financial sovereignty. But outdated and clunky interfaces make it difficult, especially on mobile devices. [bitcoin-core/gui-qml](https://github.com/bitcoin-core/gui), a project [Go Qu](https://github.com/goqusan) will contribute to, modernizes Bitcoin Core’s interface to be more accessible and mobile-friendly. By lowering the barriers to node operation, this project empowers more people — especially under autocracies in Africa, where mobile phones dominate — to strengthen their financial sovereignty. With HRF support, bitcoin-core/gui-qml is expanding node access, supporting Bitcoin’s decentralization, and reinforcing its censorship resistance for the long term. - **Rkrux** As an open-source project, Bitcoin Core relies on free and open-source developers to maintain its integrity, security, and resilience against potential threats. [Rkrux](https://github.com/rkrux), a Bitcoin Core developer, plays a crucial role by reviewing code, testing releases, and improving documentation to keep Bitcoin Core robust, secure, and censorship-resistant. Rkurx’s work identifies vulnerabilities, refines changes, and strengthens Bitcoin’s long-term stability. With HRF support, Rkrux is deepening his contributions, reinforcing Bitcoin’s foundation, and ensuring it remains a financial lifeline for human rights defenders worldwide. - **Elsat** As online censorship intensifies, free speech and financial freedom are under threat. Nostr developer [Elsat](https://github.com/alltheseas) is working to defend these freedoms by contributing to [Damus](https://github.com/damus-io), [Nostrability](https://github.com/nostrability), and [Zap.store](https://github.com/zapstore) — projects that empower individuals to communicate and transact without centralized control. Damus enables private, censorship-resistant messaging; Nostrability improves app interoperability; and Zap.store helps free and open-source software (FOSS) developers distribute and monetize their work peer-to-peer. With HRF support, Elsat is strengthening tools that protect free speech for dissidents under oppressive environments. - **Relay Wizard** Nostr, a decentralized communication protocol, relies on a network of relays (servers that pass messages between users). But setting up relays can be complex and intimidating. [Relay Wizard,](https://github.com/nodetec/relaywizard) a tool created by software developer [J the Code Monkey](https://github.com/jchiarulli), simplifies this process by automating relay setup. This allows anyone to run a relay, reduces reliance on intermediaries, and helps keep nostr resilient against online speech censorship. With HRF support, J the Code Monkey will expand development and operations, ensuring nostr remains a secure, uncensorable communication platform accessible to everyone. - **Waye** Censorship-resistant technology is essential to protecting global freedom. Yet open-source developers often operate like solo entrepreneurs — juggling engineering, project management, and community-building on their own. This leads to inefficiency, isolation, and burnout. [Waye](http://waye.dev) addresses this gap by providing psycho-social support for developers working on freedom tech. Led by Bitcoin Core developer Amiti Uttarwar and operational architect Anna Sides, Waye strengthens the human infrastructure of open source. With HRF support, Waye will support developers from global majority countries, empowering them to build the tools their fellow citizens need. - **Hashpool** Centralization in Bitcoin mining threatens its censorship resistance and makes it harder for small-scale miners to compete. [Hashpool](https://github.com/vnprc/hashpool), a self-hosted mining pool by developer [vnprc](https://github.com/vnprc), eliminates reliance on centralized entities while giving miners more control over their earnings. Instead of traditional mining pool payouts, Hashpool rewards participants with ecash tokens — digital cash that enables instant, private transactions. This ensures miners receive payouts instantly while preserving their financial privacy. It also helps keep mining open and decentralized. With HRF support, vnprc will further develop Hashpool and help resist mining centralization. - **Cashu KVAC** As dictators ramp up financial surveillance to threaten dissidents, protecting financial privacy is more critical than ever. [Cashu KVAC](https://github.com/lollerfirst/cashu-kvac) is a software upgrade for Cashu — a Chaumian ecash-based system that enables extremely strong financial privacy. Developed by [lollerfirst](https://github.com/lollerfirst), it improves privacy and efficiency by reducing wallet data storage and concealing transaction amounts from third parties. These improvements strengthen ecash functionality, safeguarding financial privacy for individuals and nonprofits alike. With HRF support, lollerfirst will develop Cashu KVAC and help protect digital and financial freedom for those living under the watchful eyes of dictators. - **Self-Custody Research** In unstable economies and under authoritarian regimes, self-custodial Bitcoin is a financial lifeline — portable money that cannot be seized, censored, or debased. While Bitcoin enables financial freedom, scaling self-custody remains a challenge. Bitcoin educator and developer [Brandon Black](https://github.com/reardencode) (Rearden) is researching these limitations and exploring technical solutions to make self-custody more accessible. His work documents the obstacles users face today and provides insights into how Bitcoin can evolve. With HRF support, Black will expand self-custody education, equipping individuals under dictatorships with the knowledge and tools to secure their financial independence. - **Stable Channels** For citizens living under authoritarian regimes and struggling economies, Bitcoin is a lifeline — but its volatility can threaten short-term financial security. [Stable Channels](https://github.com/toneloc/stable-channels/), created by software engineer [Tony Klausing](https://tonyklausing.com/), brings stabilized Bitcoin-backed balances to the Lightning Network (allowing users to peg Bitcoin to fiat currencies in a self-custodial way). This innovation enables individuals to transact freely without exposure to wild price swings or to centralized stablecoins. HRF’s support will help expand Stable Channels development, ecash integrations, and community outreach — helping more individuals harness Bitcoin’s power while maintaining financial stability. - **Bitsacco** In Kenya, Savings and Credit Cooperative Organizations (SACCOs) provide savings and lending services to their communities. But reliance on traditional banks limits their autonomy. [Bitsacco](https://github.com/bitsacco/os), created by developer [okjodom](https://github.com/okjodom), reinvents SACCOs by leveraging Bitcoin and Fedimints (a community-based custody model in Bitcoin). In this way, Bitsacco offers a more open, inclusive, and self-sustaining financial option. By reducing dependence on banks, Bitsacco empowers communities to manage their savings and loans independently. With HRF support, Bitsacco will provide a secure, familiar path to sound money in a region where financial instability and restricted access are persistent challenges. - **The Core** In Africa, where financial literacy gaps persist, hands-on Bitcoin education is crucial for adoption. [The Core](https://github.com/thecore21m-btc), founded by Kenyan Bitcoin educator [Felix Mukungu](https://x.com/MukunguFelix), bridges this gap by equipping Africans with the knowledge and skills to use Bitcoin confidently. Through hands-on training in self-custody, Lightning wallets, and Bitcoin nodes, The Core empowers individuals to take control of their money and transact freely. This grant will help expand The Core’s monthly meetups, online courses, and student-support programs — bringing Bitcoin education to more individuals across Kenya and the wider African continent. - **Bitcoin Babies** Under many authoritarian regimes, infant malnutrition is exacerbated and puts countless children at risk. [Bitcoin Babies](https://bitcoinbabies.com/), founded by [Naomi Wambui](https://x.com/NgachaNaomi1), is a project that tackles this issue by combining infant nutrition education with Bitcoin-based financial literacy. Through weekly Bitcoin stipends, financial literacy training, and community support, mothers under authoritarian rule gain the tools needed to improve their children’s health while achieving long-term financial stability. With this grant, Bitcoin Babies will expand its impact, helping more at-risk communities with resources that are otherwise unavailable and inaccessible, empowering mothers to build brighter futures. - **East Asia Bitcoin Developer Apprenticeship Program** In East Asia, language barriers and limited mentorship have made open-source Bitcoin development inaccessible to many. The [East Asia Bitcoin Developer Apprenticeship Program](https://x.com/kcalvinalvinn), led by Bitcoin developer [Calvin Kim](https://x.com/kcalvinalvinn), is changing that by creating a pathway for Korean and Japanese developers to enter the field. Through hands-on training, mentees gain practical experience, contribute to open-source projects, and eventually become mentors — strengthening the region’s developer ecosystem. With this funding, the apprenticeship program will expand, diversify Bitcoin’s global developer base, make freedom technology more accessible across Asia, and forge links with North Korean defectors. - **Bitcoin Week at TalentLand 2025** Across Latin America, government overreach threatens financial freedom. At [TalentLand 2025](https://talent-land.mx/), Latin America’s largest tech event, Bitcoin Week will demonstrate how Bitcoin empowers individuals to reclaim their financial sovereignty. Led by developer [Super Testnet](https://github.com/supertestnet) and the Bitcoin and Lightning Guadalajara community, this initiative educates Mexico’s tech community on Bitcoin’s role in fostering financial sovereignty. Through workshops, hackathons, and debates, it nurtures developer talent and engages future tech leaders. With this funding, Bitcoin Week will help expand awareness of Bitcoin’s power to resist financial oppression and accelerate Bitcoin adoption across Latin America. - **Base58** Learning Bitcoin’s technical aspects can feel overwhelming. [Base58’s Bitcoin Live Action Role Play](https://github.com/base58btc/LARP) (LARP) simplifies this with a two-hour workshop where participants act out the Bitcoin network and see how transactions are made, how they get to miners, the work a Bitcoin node does, and how it helps secure the network. Created by [Lisa Neigut](https://x.com/niftynei) (niftynei), a prolific Bitcoin developer, educator, and founder of [Base58](https://base58.school/) and the [bitcoin++](https://btcplusplus.dev/) conference, alongside David Rodriguez, this immersive experience makes Bitcoin education tangible and entertaining. Now expanding beyond North America, it will train new facilitators, prioritizing regions with limited Bitcoin education due to authoritarian restrictions. With this funding, Base58 Bitcoin LARP will equip more facilitators to teach and learn Bitcoin in an engaging, accessible way. - **BTCenEspañol** Across Latin America, financial repression and limited access to Bitcoin education leave many without the tools to navigate financial repression. [BTCenEspañol](https://www.btcenespanol.com/) has been a leader in Spanish-language Bitcoin education since 2014. With a goal of reaching one million learners and training 100 teachers, BTCenEspañol is expanding to make Bitcoin education more accessible across the region, especially in places like Nicaragua and Venezuela. HRF’s grant will support this growth, equipping individuals with the knowledge to secure their financial independence amid rising authoritarianism in the continent. - **Increasing nonprofit Adoption of Bitcoin** Under dictatorships, non-governmental organizations face frozen bank accounts, surveillance, and financial censorship — limiting their ability to support vulnerable communities. Bitcoin researcher [Daniel Batten](https://x.com/dsbatten) is quantifying Bitcoin’s role as a financial lifeline to help nonprofits overcome these challenges. Through empirical research, his initiative will show how Bitcoin enables nonprofits under authoritarian regimes to operate more freely. With this grant, the project will equip nonprofits in closed societies with the knowledge and tools to integrate Bitcoin into their operations, strengthening their financial resilience and advancing global movements. - **Bitcoin for Good** When authoritarian regimes weaponize the financial system against dissent, nonprofits and charities are among the first to suffer. Bitcoin for Good is an educational initiative led by activist and Groundswell founder [Hadiya Masieh](https://www.groundswellproject.org/about/who-we-are/). It helps organizations break free by teaching them how to accept and manage censorship-resistant funding. Through hands-on training and direct integration with Bitcoin for donations, nonprofits learn to operate outside the reach of financial gatekeepers and regimes. With this grant, Bitcoin for Good will help nonprofits stay funded, independent, and free to continue their work. About BDF HRF’s Bitcoin Development Fund (BDF) supports individuals and projects that make Bitcoin and related freedom technologies more powerful tools for human rights defenders operating in challenging political and financial environments. Since launching in 2020, BDF has gifted $7.8 million in BTC to 284 projects across 62 countries worldwide. The next round of grants will be announced at the 17th annual Oslo Freedom Forum, taking place May 26-28, 2025, in Oslo, Norway. Learn more about HRF’s Bitcoin Development Fund on our website. ### About BDF HRF’s Bitcoin Development Fund (BDF) supports individuals and projects that make Bitcoin and related freedom technologies more powerful tools for human rights defenders operating in challenging political and financial environments. Since launching in 2020, BDF has gifted $7.8 million in BTC to 284 projects across 62 countries worldwide. The next round of grants will be announced at the [17th annual Oslo Freedom Forum](http://oslofreedomforum.com), taking place May 26-28, 2025, in Oslo, Norway. Learn more about HRF’s Bitcoin Development Fund on our [website](https://hrf.org/program/financial-freedom/bitcoin-development-fund/). *HRF is a registered 501(c)(3) nonprofit organization. Donations are tax-deductible to the fullest extent allowable by law. Gifts can be made at [HRF.org/DevFund](https://hrf.org/devfund), and proposals for support can be submitted to [https://hrf.org/bdfapply](https://hrf.org/bdfapply).* *Follow [@HRF](https://twitter.com/HRF) on X for more updates on this project and all of our other programs designed to promote freedom and human rights around the world.*
@ f1989a96:bcaaf2c1
2025-04-01 14:31:43**NEW YORK** (April 1,2025) — The Human Rights Foundation (HRF) is pleased to announce 1 billion satoshis of gifts from its [Bitcoin Development Fund](https://hrf.org/devfund). HRF’s latest batch of grants supports open-source development, educational initiatives, mining decentralization, and privacy tools for activists living under authoritarian regimes across Latin America, Africa, and Asia. The gifts also further promote Internet freedom and decentralized communications, ensuring dissidents can connect, communicate, organize, and transact without censorship. Quarter 1 2025 grantees include: - **NetBlocks** Authoritarian regimes weaponize Internet shutdowns to silence dissent, restrict information, and cut off financial lifelines. By blocking communication channels, they isolate individuals, suppress independent media, and disrupt financial flows. [NetBlocks](https://netblocks.org/) exposes these digital crackdowns in real time, ensuring the world sees and responds to digital repression. Through continuous monitoring, it equips activists, journalists, and civil society with the data needed to challenge censorship and advocate for an open internet. With HRF support, NetBlocks will expand its monitoring, documentation, and research — reinforcing internet and financial freedom as a critical human rights safeguard. - **TollGate** Authoritarian regimes exploit Internet Service Providers (ISPs) to monitor and suppress dissent, undermining online privacy essential for human rights defenders. [TollGate](https://opentollgate.github.io/tollgate/), developed by c03rad0r, is software that transforms any WiFi router into a permissionless Internet Service Provider (ISP) using Bitcoin and ecash. By decentralizing Internet access and turning any WiFi router into part of a peer-to-peer, private, open internet network, Tollgate helps resist authoritarian surveillance and protect digital freedoms. With HRF support, TollGate is advancing an open, accessible, and censorship-proof internet for those who need it most. - **Vinteum** Across Latin America, authoritarian regimes restrict financial access to tighten their grip on power. But a growing network of developers is working to change that. [Vinteum](https://vinteum.org/), a nonprofit Bitcoin research and development center led by executive director [Lucas Ferreira](https://x.com/lucasdcf), trains and funds developers to strengthen Bitcoin as a tool for financial freedom. Through education, development, and community building, Vinteum fosters local talent and expands regional Bitcoin accessibility. With HRF support, Vinteum will scale its programs and help more Latin Americans achieve financial independence. - **BTCPay Server** Dictators often block payment processors to cripple the work of nonprofits and dissidents. [BTCPay Server](https://btcpayserver.org/), a self-hosted, open-source Bitcoin payment processor, now breaks this control. It provides individuals, nonprofits, and merchants with a censorship-resistant way to accept payments. Activists and nonprofits can now process global payments, launch crowdfunding campaigns, and build movements on Bitcoin — all without third parties or restrictions. With HRF support, BTCPay Server will expand access to self-custodial payments, enabling more organizations under dictatorships to transact freely. - **Africa Bitcoin Institute (ABI)** Across Africa, dictators manipulate financial institutions to retain control, while more than half the population remains unbanked. Bitcoin offers an alternative, but without proper research, education, and policy frameworks, adoption remains limited. The Africa Bitcoin Institute (ABI), supported by the Rwandan human rights activist [Anaïse Kanimba](https://x.com/AnaiseKanimba), is launching to bridge this gap. Through evidence-based research and policy recommendations, ABI will equip policymakers with the knowledge and tools to integrate Bitcoin into African economies. With HRF support, ABI will promote financial autonomy and solidify Bitcoin’s role as a pillar of economic freedom. - **Bitcoin Core Graphical User Interface** Running a Bitcoin node (software that enables users to verify transitions and enforce the network’s rules) is key to financial sovereignty. But outdated and clunky interfaces make it difficult, especially on mobile devices. [bitcoin-core/gui-qml](https://github.com/bitcoin-core/gui), a project [Go Qu](https://github.com/goqusan) will contribute to, modernizes Bitcoin Core’s interface to be more accessible and mobile-friendly. By lowering the barriers to node operation, this project empowers more people — especially under autocracies in Africa, where mobile phones dominate — to strengthen their financial sovereignty. With HRF support, bitcoin-core/gui-qml is expanding node access, supporting Bitcoin’s decentralization, and reinforcing its censorship resistance for the long term. - **Rkrux** As an open-source project, Bitcoin Core relies on free and open-source developers to maintain its integrity, security, and resilience against potential threats. [Rkrux](https://github.com/rkrux), a Bitcoin Core developer, plays a crucial role by reviewing code, testing releases, and improving documentation to keep Bitcoin Core robust, secure, and censorship-resistant. Rkurx’s work identifies vulnerabilities, refines changes, and strengthens Bitcoin’s long-term stability. With HRF support, Rkrux is deepening his contributions, reinforcing Bitcoin’s foundation, and ensuring it remains a financial lifeline for human rights defenders worldwide. - **Elsat** As online censorship intensifies, free speech and financial freedom are under threat. Nostr developer [Elsat](https://github.com/alltheseas) is working to defend these freedoms by contributing to [Damus](https://github.com/damus-io), [Nostrability](https://github.com/nostrability), and [Zap.store](https://github.com/zapstore) — projects that empower individuals to communicate and transact without centralized control. Damus enables private, censorship-resistant messaging; Nostrability improves app interoperability; and Zap.store helps free and open-source software (FOSS) developers distribute and monetize their work peer-to-peer. With HRF support, Elsat is strengthening tools that protect free speech for dissidents under oppressive environments. - **Relay Wizard** Nostr, a decentralized communication protocol, relies on a network of relays (servers that pass messages between users). But setting up relays can be complex and intimidating. [Relay Wizard,](https://github.com/nodetec/relaywizard) a tool created by software developer [J the Code Monkey](https://github.com/jchiarulli), simplifies this process by automating relay setup. This allows anyone to run a relay, reduces reliance on intermediaries, and helps keep nostr resilient against online speech censorship. With HRF support, J the Code Monkey will expand development and operations, ensuring nostr remains a secure, uncensorable communication platform accessible to everyone. - **Waye** Censorship-resistant technology is essential to protecting global freedom. Yet open-source developers often operate like solo entrepreneurs — juggling engineering, project management, and community-building on their own. This leads to inefficiency, isolation, and burnout. [Waye](http://waye.dev) addresses this gap by providing psycho-social support for developers working on freedom tech. Led by Bitcoin Core developer Amiti Uttarwar and operational architect Anna Sides, Waye strengthens the human infrastructure of open source. With HRF support, Waye will support developers from global majority countries, empowering them to build the tools their fellow citizens need. - **Hashpool** Centralization in Bitcoin mining threatens its censorship resistance and makes it harder for small-scale miners to compete. [Hashpool](https://github.com/vnprc/hashpool), a self-hosted mining pool by developer [vnprc](https://github.com/vnprc), eliminates reliance on centralized entities while giving miners more control over their earnings. Instead of traditional mining pool payouts, Hashpool rewards participants with ecash tokens — digital cash that enables instant, private transactions. This ensures miners receive payouts instantly while preserving their financial privacy. It also helps keep mining open and decentralized. With HRF support, vnprc will further develop Hashpool and help resist mining centralization. - **Cashu KVAC** As dictators ramp up financial surveillance to threaten dissidents, protecting financial privacy is more critical than ever. [Cashu KVAC](https://github.com/lollerfirst/cashu-kvac) is a software upgrade for Cashu — a Chaumian ecash-based system that enables extremely strong financial privacy. Developed by [lollerfirst](https://github.com/lollerfirst), it improves privacy and efficiency by reducing wallet data storage and concealing transaction amounts from third parties. These improvements strengthen ecash functionality, safeguarding financial privacy for individuals and nonprofits alike. With HRF support, lollerfirst will develop Cashu KVAC and help protect digital and financial freedom for those living under the watchful eyes of dictators. - **Self-Custody Research** In unstable economies and under authoritarian regimes, self-custodial Bitcoin is a financial lifeline — portable money that cannot be seized, censored, or debased. While Bitcoin enables financial freedom, scaling self-custody remains a challenge. Bitcoin educator and developer [Brandon Black](https://github.com/reardencode) (Rearden) is researching these limitations and exploring technical solutions to make self-custody more accessible. His work documents the obstacles users face today and provides insights into how Bitcoin can evolve. With HRF support, Black will expand self-custody education, equipping individuals under dictatorships with the knowledge and tools to secure their financial independence. - **Stable Channels** For citizens living under authoritarian regimes and struggling economies, Bitcoin is a lifeline — but its volatility can threaten short-term financial security. [Stable Channels](https://github.com/toneloc/stable-channels/), created by software engineer [Tony Klausing](https://tonyklausing.com/), brings stabilized Bitcoin-backed balances to the Lightning Network (allowing users to peg Bitcoin to fiat currencies in a self-custodial way). This innovation enables individuals to transact freely without exposure to wild price swings or to centralized stablecoins. HRF’s support will help expand Stable Channels development, ecash integrations, and community outreach — helping more individuals harness Bitcoin’s power while maintaining financial stability. - **Bitsacco** In Kenya, Savings and Credit Cooperative Organizations (SACCOs) provide savings and lending services to their communities. But reliance on traditional banks limits their autonomy. [Bitsacco](https://github.com/bitsacco/os), created by developer [okjodom](https://github.com/okjodom), reinvents SACCOs by leveraging Bitcoin and Fedimints (a community-based custody model in Bitcoin). In this way, Bitsacco offers a more open, inclusive, and self-sustaining financial option. By reducing dependence on banks, Bitsacco empowers communities to manage their savings and loans independently. With HRF support, Bitsacco will provide a secure, familiar path to sound money in a region where financial instability and restricted access are persistent challenges. - **The Core** In Africa, where financial literacy gaps persist, hands-on Bitcoin education is crucial for adoption. [The Core](https://github.com/thecore21m-btc), founded by Kenyan Bitcoin educator [Felix Mukungu](https://x.com/MukunguFelix), bridges this gap by equipping Africans with the knowledge and skills to use Bitcoin confidently. Through hands-on training in self-custody, Lightning wallets, and Bitcoin nodes, The Core empowers individuals to take control of their money and transact freely. This grant will help expand The Core’s monthly meetups, online courses, and student-support programs — bringing Bitcoin education to more individuals across Kenya and the wider African continent. - **Bitcoin Babies** Under many authoritarian regimes, infant malnutrition is exacerbated and puts countless children at risk. [Bitcoin Babies](https://bitcoinbabies.com/), founded by [Naomi Wambui](https://x.com/NgachaNaomi1), is a project that tackles this issue by combining infant nutrition education with Bitcoin-based financial literacy. Through weekly Bitcoin stipends, financial literacy training, and community support, mothers under authoritarian rule gain the tools needed to improve their children’s health while achieving long-term financial stability. With this grant, Bitcoin Babies will expand its impact, helping more at-risk communities with resources that are otherwise unavailable and inaccessible, empowering mothers to build brighter futures. - **East Asia Bitcoin Developer Apprenticeship Program** In East Asia, language barriers and limited mentorship have made open-source Bitcoin development inaccessible to many. The [East Asia Bitcoin Developer Apprenticeship Program](https://x.com/kcalvinalvinn), led by Bitcoin developer [Calvin Kim](https://x.com/kcalvinalvinn), is changing that by creating a pathway for Korean and Japanese developers to enter the field. Through hands-on training, mentees gain practical experience, contribute to open-source projects, and eventually become mentors — strengthening the region’s developer ecosystem. With this funding, the apprenticeship program will expand, diversify Bitcoin’s global developer base, make freedom technology more accessible across Asia, and forge links with North Korean defectors. - **Bitcoin Week at TalentLand 2025** Across Latin America, government overreach threatens financial freedom. At [TalentLand 2025](https://talent-land.mx/), Latin America’s largest tech event, Bitcoin Week will demonstrate how Bitcoin empowers individuals to reclaim their financial sovereignty. Led by developer [Super Testnet](https://github.com/supertestnet) and the Bitcoin and Lightning Guadalajara community, this initiative educates Mexico’s tech community on Bitcoin’s role in fostering financial sovereignty. Through workshops, hackathons, and debates, it nurtures developer talent and engages future tech leaders. With this funding, Bitcoin Week will help expand awareness of Bitcoin’s power to resist financial oppression and accelerate Bitcoin adoption across Latin America. - **Base58** Learning Bitcoin’s technical aspects can feel overwhelming. [Base58’s Bitcoin Live Action Role Play](https://github.com/base58btc/LARP) (LARP) simplifies this with a two-hour workshop where participants act out the Bitcoin network and see how transactions are made, how they get to miners, the work a Bitcoin node does, and how it helps secure the network. Created by [Lisa Neigut](https://x.com/niftynei) (niftynei), a prolific Bitcoin developer, educator, and founder of [Base58](https://base58.school/) and the [bitcoin++](https://btcplusplus.dev/) conference, alongside David Rodriguez, this immersive experience makes Bitcoin education tangible and entertaining. Now expanding beyond North America, it will train new facilitators, prioritizing regions with limited Bitcoin education due to authoritarian restrictions. With this funding, Base58 Bitcoin LARP will equip more facilitators to teach and learn Bitcoin in an engaging, accessible way. - **BTCenEspañol** Across Latin America, financial repression and limited access to Bitcoin education leave many without the tools to navigate financial repression. [BTCenEspañol](https://www.btcenespanol.com/) has been a leader in Spanish-language Bitcoin education since 2014. With a goal of reaching one million learners and training 100 teachers, BTCenEspañol is expanding to make Bitcoin education more accessible across the region, especially in places like Nicaragua and Venezuela. HRF’s grant will support this growth, equipping individuals with the knowledge to secure their financial independence amid rising authoritarianism in the continent. - **Increasing nonprofit Adoption of Bitcoin** Under dictatorships, non-governmental organizations face frozen bank accounts, surveillance, and financial censorship — limiting their ability to support vulnerable communities. Bitcoin researcher [Daniel Batten](https://x.com/dsbatten) is quantifying Bitcoin’s role as a financial lifeline to help nonprofits overcome these challenges. Through empirical research, his initiative will show how Bitcoin enables nonprofits under authoritarian regimes to operate more freely. With this grant, the project will equip nonprofits in closed societies with the knowledge and tools to integrate Bitcoin into their operations, strengthening their financial resilience and advancing global movements. - **Bitcoin for Good** When authoritarian regimes weaponize the financial system against dissent, nonprofits and charities are among the first to suffer. Bitcoin for Good is an educational initiative led by activist and Groundswell founder [Hadiya Masieh](https://www.groundswellproject.org/about/who-we-are/). It helps organizations break free by teaching them how to accept and manage censorship-resistant funding. Through hands-on training and direct integration with Bitcoin for donations, nonprofits learn to operate outside the reach of financial gatekeepers and regimes. With this grant, Bitcoin for Good will help nonprofits stay funded, independent, and free to continue their work. About BDF HRF’s Bitcoin Development Fund (BDF) supports individuals and projects that make Bitcoin and related freedom technologies more powerful tools for human rights defenders operating in challenging political and financial environments. Since launching in 2020, BDF has gifted $7.8 million in BTC to 284 projects across 62 countries worldwide. The next round of grants will be announced at the 17th annual Oslo Freedom Forum, taking place May 26-28, 2025, in Oslo, Norway. Learn more about HRF’s Bitcoin Development Fund on our website. ### About BDF HRF’s Bitcoin Development Fund (BDF) supports individuals and projects that make Bitcoin and related freedom technologies more powerful tools for human rights defenders operating in challenging political and financial environments. Since launching in 2020, BDF has gifted $7.8 million in BTC to 284 projects across 62 countries worldwide. The next round of grants will be announced at the [17th annual Oslo Freedom Forum](http://oslofreedomforum.com), taking place May 26-28, 2025, in Oslo, Norway. Learn more about HRF’s Bitcoin Development Fund on our [website](https://hrf.org/program/financial-freedom/bitcoin-development-fund/). *HRF is a registered 501(c)(3) nonprofit organization. Donations are tax-deductible to the fullest extent allowable by law. Gifts can be made at [HRF.org/DevFund](https://hrf.org/devfund), and proposals for support can be submitted to [https://hrf.org/bdfapply](https://hrf.org/bdfapply).* *Follow [@HRF](https://twitter.com/HRF) on X for more updates on this project and all of our other programs designed to promote freedom and human rights around the world.* @ 5d4b6c8d:8a1c1ee3
2025-04-01 13:41:45I'm trying out a new month-long focus. For Active April, I'm going to be more proactive about doing stuff around the house that needs doing. It's gonna get all Jordan Peterson cleaning your room up in here. Let's see how noticeable the consequences are. - I predict a happier wife, for one. - I'm also curious to see what kind of fitness impacts there are to increasing this kind of activity, compared to doing more exercise. originally posted at https://stacker.news/items/931099
@ 5d4b6c8d:8a1c1ee3
2025-04-01 13:41:45I'm trying out a new month-long focus. For Active April, I'm going to be more proactive about doing stuff around the house that needs doing. It's gonna get all Jordan Peterson cleaning your room up in here. Let's see how noticeable the consequences are. - I predict a happier wife, for one. - I'm also curious to see what kind of fitness impacts there are to increasing this kind of activity, compared to doing more exercise. originally posted at https://stacker.news/items/931099 @ fd78c37f:a0ec0833
2025-04-01 11:49:06In this edition, we invited Keypleb, the founder of Bitcoin Indonesia, to share how he built the Bitcoin community in Indonesia, overcoming challenges like member turnover and venue selection, while driving the adoption and growth of Bitcoin. **YakiHonne**: Welcome, Keypleb. Before we begin, let me briefly introduce YakiHonne. YakiHonne is a decentralized media client built on Nostr—a protocol designed to empower freedom of speech through technology. It enables creators to own their voices and assets while offering innovative tools like smart widgets, verified notes, and support for long-form content. We focus on free speech and free media by user privacy and data to be protected. So before starting the interview, I'd like to hear about yourself and your community. **Keypleb**:My name is Keypleb, though it’s a pseudonym—a name I use to respect privacy. I'm a co-founder of Bitcoin Indonesia, Bitcoin House Bali, and Code Orange, a new developer school we launched at a conference just a few days ago. We focus on driving adoption through meetups, hackathons, and technical workshops. I'll dive into more details later, but that's a brief overview. I'm based in Bali now, though I travel a lot and consider myself quite nomadic. Great to be here. **YakiHonne**: What sparked your interest in Bitcoin and what motivated you to create a community on Bitcoin? **Keypleb**:I first got interested in Bitcoin because it solved a specific problem. At the time, I didn’t know exactly what the solution was, but the problem was that I couldn’t afford a home. Back in 2019, I was living in London, and a two-bedroom apartment was £600,000, which was insanely expensive. First-time buyers like myself simply couldn’t afford it. Why was it so expensive? Why was buying a house so hard? During the COVID lockdown, I had more time on my hands and started listening to Michael Saylor on a Bitcoin podcast, where he talked about how the system is rigged, and that’s why people work hard but still can’t afford a house. That really resonated with me. So I started looking for a community, but unfortunately, there wasn’t one.. **Keypleb**:After moving to Bali, I attended a lot of crypto meetups, especially scammy altcoin ones, thinking, “There has to be a solution.” But none of them resonated with me. There was no sense of freedom, and no real discussion about inflation resistance. I remembered a podcast from Dea Reskita, an Indonesian host who’s pretty well-known online. I reached out to her and said, “ you’ve got to help me. I’m surrounded by all these shitcoiners, and I can’t take it anymore. I need a real community. Is anything happening?” She replied, “Yes, something is happening. We should restart these meetups next month.” And that’s how it all began. **Keypleb**:There’s also another story about how we started Bitcoin House and how Bitcoin in Asia came to be, but maybe I’ll save that for later. Anyway, the spark of interest came from Bitcoin solving a real problem, and my drive to keep going came from the lack of quality meetups. Now, we’ve hosted 31 meetups, launched Bitcoin House and Code Orange, and the movement is growing rapidly.  **YakiHonne**: That’s such an amazing story—going from being on the brink of homelessness to creating something so impactful, and keeping it running every day, bringing new people into the journey. It’s truly inspiring. I’m curious about how the community started. How did you manage to attract members and build a strong community? What challenges did you face along the way? **Keypleb**:It all started with our first meetup at the end of 2022, which was two and a half years ago now. At that time, we sent out an email to a group from a previous database, and the first meetup had around 20 people, which was a good start. However, problems quickly arose as people started dropping off, and the community lacked retention. In Bali, people come and go, usually staying for no more than two months, leading to a lack of long-term participation. This became one of our challenges: how to attract more people and, more importantly, get the same people to keep coming back. While I've been coming back for two and a half years, not everyone is able to return as often, and that has been a real challenge. **Keypleb**:Actually, I should also mention how I met my co-founders—Marius, Diana, and Dimas. We met at the 2023 Indonesia Bitcoin Conference. As time went on, we kept hosting meetups and had a lot of fun each time, though the locations kept changing. One of the initial challenges was that we didn't realize the importance of having a fixed meetup location. We changed venues several times before we realized that having a consistent location is crucial. If anyone wants to run a meetup, it's best to always choose a fixed location. We learned this through trial and error, but now it's no longer an issue. **Keypleb**:Since the conference, my co-founders and I have been working together, consistently putting in the effort. This is why our community has grown so large—so far, we are hosting 31 monthly meetups, 6 of which are in Bali. This means there is a bitcoin meetup almost every day on a regular basis. We've also established Bitcoin House Bali, a physical space, and the movement is growing rapidly. Without this movement, the region would face many challenges, including inflation and heavy censorship. It all started from just one meetup.  **YakiHonne**: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now? **Keypleb**:First, one very important piece of advice is to ensure that every meetup is held at the same location regularly. We realized this challenge through trial and error. To help others who are interested, we’ve published our meetup guide on GitHub, where everyone can check it out. For example, meetups should be held regularly, ideally once a month, or even once a week. In Chiang Mai, the Bitcoin meetup starts every Thursday at 7 PM, and everyone knows the time and location, making it easy to join without having to look up the next meetup. **Keypleb**:Additionally, our meetup structure is very simple. First, we do a round of introductions where everyone shares their name, where they’re from, and what Bitcoin means to them. This usually takes about 15 minutes. Then, we discuss three main questions: First, why do we need Bitcoin? The discussion typically focuses on two main issues Bitcoin addresses: inflation and censorship;Secondly, how to buy Bitcoin? We usually ask who wants to buy some Bitcoin, and then we do a small purchase together and conduct a P2P trade to demonstrate how easy it is to buy Bitcoin. Lastly, how to store Bitcoin? We introduce self-custody and show how to use hardware wallets (like Trezor), explaining the concept of the 12 words and private keys. **Keypleb**:The whole meetup usually wraps up in about an hour, after which people can continue socializing at Bitcoin House or wherever the meetup is taking place. In short, keeping the meetup simple and efficient, and ensuring a fixed location for each event, are key factors in building a successful community. **YakiHonne**: What's the major approach? Is it more technical, or do you focus on non-technical aspects, or do you cover both? **Keypleb**:Our approach includes both technical and non-technical content. Initially, our meetups were completely non-technical, just casual gatherings for people to socialize. Over time, however, we've evolved to incorporate more technical content. **Keypleb**:Out of the 31 monthly regular meetups we host, most of them have been non-technical, simply regular gatherings held at the same time and place according to our meetup guide. For example, we host the “Bitcoin for Beginners” meetup, which is designed for newcomers and takes place every second Friday of the month at 5 PM at the Bitcoin House Bali. This is entirely non-technical. Additionally, every Wednesday at Bitcoin House, we host the “My First Bitcoin” course. While the course touches on some technical aspects, such as seed phrases and backups, it’s still beginner-friendly and not too technical. The course runs for 10 weeks, and we plan to offer it in the local language at Bali University to help the local community better understand Bitcoin. **Keypleb**:On the other hand, we also offer highly technical content. We launched a new program called “Code Orange,” which is specifically designed for developers and programmers. We use the “Decoding Bitcoin” website, created by Jamal, which is a learning platform for developers. Many developer schools, like Code Orange, use this resource. Additionally, we host “Code Orange” meetups where we dive into the technical aspects of Bitcoin, such as how mining works and how to prevent single points of failure. **Keypleb**:We also organize technical workshops, such as “How to Defend Against a Five-Dollar Wrench Attack,” which is closely related to security. Recently, there have been some kidnapping incidents in Bali, and many people are concerned about their Bitcoin being stolen. To address this, we plan to hold a workshop on how to protect Bitcoin against such attacks. Additionally, we host hackathons and other high-tech events, and we just completed a very successful beginner-level hackathon. **Keypleb**:In summary, our community caters to everyone, from beginners to technical experts. For beginners, we offer easy-to-understand, non-technical content, while for experienced Bitcoiners, we provide in-depth technical material.  **YakiHonne**: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved? **Keypleb**:I have some additional advice. First, technical individuals can sign up for the “Decoding Bitcoin” course that starts on 18th March 2025 or join our “Code Orange” program and participate in the end-of-year hackathon. If they are technically proficient, this will be a great opportunity. “Decoding Bitcoin” is great for beginners, but it’s also useful for technical individuals. If someone is very skilled, they can start contributing code right away. If they find the course too easy, they can skip it and dive directly into more advanced projects. Additionally, Bitshala and Chaincode Labs offer advanced courses, which more technically advanced individuals can choose to pursue.  **Keypleb**:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash. **YakiHonne**: I’d like to move on to the next question: How do you see Bitcoin communities evolving as technology progresses, particularly in areas like scalability, privacy, and adaptability to other systems? Keypleb:I believe the Bitcoin community will continue to evolve, and it has already made incredible progress. Two and a half years ago, we started alone in Bali, with just ourselves. We began in the official phase and have had numerous conversations throughout the year. For example, we are now starting a Bitcoin club at a university in Bali; we just need to find a passionate, driven “Bitcoin maximalist,” and the Bitcoin club will begin. Like what our friends did in Banyuwangi, Indonesia, these clubs could eventually evolve into Bitcoin houses. **Keypleb**:Regarding privacy and scalability, the community is making strides. We’re big fans of Fedi, which builds on top of the Fedimint protocol and uses e-cash to scale Bitcoin while improving privacy. Fedi low fees and high privacy potential give Bitcoin great opportunities in this area. **Keypleb**:As for Bitcoin's compatibility with fiat systems, although Bitcoin payments are illegal in some countries like Indonesia, smart developers across Southeast Asia are working on legal solutions. For example, there's a website called Pleb QR that works in Thailand, allowing you to pay in fiat via the Lightning Network. Koral is another app specifically for Indonesia. These kinds of testing products already exist and are physically possible, but we’re just waiting on regulations. My influential friends are actively lobbying the government for adoption. **Keypleb**:In summary, privacy, scalability, and compatibility with fiat systems are all works in progress, and they will continue to evolve positively. There will be more meetups, more wallet downloads, and more adoption—there’s no doubt about that. **YakiHonne**: You mentioned the concept of cross-country issues, so I have one last question: How is the government’s stance on Bitcoin? Is the political climate supportive or against Bitcoin? How do you see the government's approach to Bitcoin in your community or environment? **Keypleb**:This reminds me of a person, Jeff Booth, who once said, “We are them, the government is made up of us.” In Indonesia, many politicians actually support Bitcoin, and many of them mine Bitcoin themselves. When money is involved, the incentive is strong, and politicians naturally like to make more money. As a result, Indonesia has a large Bitcoin mining scene. However, overall, the Indonesian government is against Bitcoin, as seen in their ban on Bitcoin payments. The 2011 currency law states that any currency other than the Indonesian Rupiah (IDR) cannot be used, and violators can face up to one year in prison or a fine. This means you cannot pay with US dollars, lira, euros, pesos or pounds. **Keypleb**:This shows that the government’s legal system is somewhat fragile. It’s understandable that the government is concerned about disruptive technologies like Bitcoin, especially with such a fragile fiat system. Indonesia has also seen many arrests. In 2016, Bank Indonesia issued a letter announcing a crackdown on cryptocurrency payments. Those involved in paying in Bitcoin had their funds seized, and the police cooperated in shutting down businesses accepting Bitcoin payments in the cities. While this isn't very friendly, it does highlight the fragility of the existing system. We also believe that a new executive order may be introduced in the future, similar to when President Roosevelt in 1933 ordered Americans to hand over all their gold with his Executive Order 6102. If it happened before, it could happen again. **Keypleb**:Therefore, we predict that Bitcoin custody could become a legal issue, which is one of the reasons we blur the faces of participants at every meetup. We need to protect the community from any potential risks. But overall, we remain optimistic. Despite the government ban, the ideology of Bitcoin is unstoppable, and its spread cannot be stopped. So, we are very optimistic about the future. **YakiHonne**: I think almost every government around the world, even in Africa, faces similar issues with Bitcoin. Some governments might want Bitcoin but hesitate to openly accept it due to the fear of it undermining the traditional financial system, which, of course, could eventually happen. But hopefully, as the new generation comes into power, we'll see more Bitcoin-friendly governments. So, thank you so much for sharing your insights and advice. I really appreciate your time and the valuable input you've provided. **Keypleb**:I'm really glad this conversation enlightened me. I enjoyed it a lot, and it made me reflect on how much work we're doing and how valuable it is. There are a lot of problems out there, with censorship being the biggest one, followed by inflation, which is also a major issue depending on the region. But Bitcoin is open, the community is growing, and people are fighting against censorship and internet shutdowns in places like Indonesia and beyond. The movement is definitely growing. So, I'm very happy to be here and have this chat. Thanks again. Bitcoin Indonesia nostr: nostr:npub1y4qd2zhtn05gnsaaq5xfejzfk4a32638tx6gpp9g8k6e42g9d66qaxhcr3 Keypleb nostr: nostr:npub190trvg63e6tyqlwlj6lccqpftx76lckj25c006vwx3dzvdl88yxs2nyqdx
@ fd78c37f:a0ec0833
2025-04-01 11:49:06In this edition, we invited Keypleb, the founder of Bitcoin Indonesia, to share how he built the Bitcoin community in Indonesia, overcoming challenges like member turnover and venue selection, while driving the adoption and growth of Bitcoin. **YakiHonne**: Welcome, Keypleb. Before we begin, let me briefly introduce YakiHonne. YakiHonne is a decentralized media client built on Nostr—a protocol designed to empower freedom of speech through technology. It enables creators to own their voices and assets while offering innovative tools like smart widgets, verified notes, and support for long-form content. We focus on free speech and free media by user privacy and data to be protected. So before starting the interview, I'd like to hear about yourself and your community. **Keypleb**:My name is Keypleb, though it’s a pseudonym—a name I use to respect privacy. I'm a co-founder of Bitcoin Indonesia, Bitcoin House Bali, and Code Orange, a new developer school we launched at a conference just a few days ago. We focus on driving adoption through meetups, hackathons, and technical workshops. I'll dive into more details later, but that's a brief overview. I'm based in Bali now, though I travel a lot and consider myself quite nomadic. Great to be here. **YakiHonne**: What sparked your interest in Bitcoin and what motivated you to create a community on Bitcoin? **Keypleb**:I first got interested in Bitcoin because it solved a specific problem. At the time, I didn’t know exactly what the solution was, but the problem was that I couldn’t afford a home. Back in 2019, I was living in London, and a two-bedroom apartment was £600,000, which was insanely expensive. First-time buyers like myself simply couldn’t afford it. Why was it so expensive? Why was buying a house so hard? During the COVID lockdown, I had more time on my hands and started listening to Michael Saylor on a Bitcoin podcast, where he talked about how the system is rigged, and that’s why people work hard but still can’t afford a house. That really resonated with me. So I started looking for a community, but unfortunately, there wasn’t one.. **Keypleb**:After moving to Bali, I attended a lot of crypto meetups, especially scammy altcoin ones, thinking, “There has to be a solution.” But none of them resonated with me. There was no sense of freedom, and no real discussion about inflation resistance. I remembered a podcast from Dea Reskita, an Indonesian host who’s pretty well-known online. I reached out to her and said, “ you’ve got to help me. I’m surrounded by all these shitcoiners, and I can’t take it anymore. I need a real community. Is anything happening?” She replied, “Yes, something is happening. We should restart these meetups next month.” And that’s how it all began. **Keypleb**:There’s also another story about how we started Bitcoin House and how Bitcoin in Asia came to be, but maybe I’ll save that for later. Anyway, the spark of interest came from Bitcoin solving a real problem, and my drive to keep going came from the lack of quality meetups. Now, we’ve hosted 31 meetups, launched Bitcoin House and Code Orange, and the movement is growing rapidly.  **YakiHonne**: That’s such an amazing story—going from being on the brink of homelessness to creating something so impactful, and keeping it running every day, bringing new people into the journey. It’s truly inspiring. I’m curious about how the community started. How did you manage to attract members and build a strong community? What challenges did you face along the way? **Keypleb**:It all started with our first meetup at the end of 2022, which was two and a half years ago now. At that time, we sent out an email to a group from a previous database, and the first meetup had around 20 people, which was a good start. However, problems quickly arose as people started dropping off, and the community lacked retention. In Bali, people come and go, usually staying for no more than two months, leading to a lack of long-term participation. This became one of our challenges: how to attract more people and, more importantly, get the same people to keep coming back. While I've been coming back for two and a half years, not everyone is able to return as often, and that has been a real challenge. **Keypleb**:Actually, I should also mention how I met my co-founders—Marius, Diana, and Dimas. We met at the 2023 Indonesia Bitcoin Conference. As time went on, we kept hosting meetups and had a lot of fun each time, though the locations kept changing. One of the initial challenges was that we didn't realize the importance of having a fixed meetup location. We changed venues several times before we realized that having a consistent location is crucial. If anyone wants to run a meetup, it's best to always choose a fixed location. We learned this through trial and error, but now it's no longer an issue. **Keypleb**:Since the conference, my co-founders and I have been working together, consistently putting in the effort. This is why our community has grown so large—so far, we are hosting 31 monthly meetups, 6 of which are in Bali. This means there is a bitcoin meetup almost every day on a regular basis. We've also established Bitcoin House Bali, a physical space, and the movement is growing rapidly. Without this movement, the region would face many challenges, including inflation and heavy censorship. It all started from just one meetup.  **YakiHonne**: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now? **Keypleb**:First, one very important piece of advice is to ensure that every meetup is held at the same location regularly. We realized this challenge through trial and error. To help others who are interested, we’ve published our meetup guide on GitHub, where everyone can check it out. For example, meetups should be held regularly, ideally once a month, or even once a week. In Chiang Mai, the Bitcoin meetup starts every Thursday at 7 PM, and everyone knows the time and location, making it easy to join without having to look up the next meetup. **Keypleb**:Additionally, our meetup structure is very simple. First, we do a round of introductions where everyone shares their name, where they’re from, and what Bitcoin means to them. This usually takes about 15 minutes. Then, we discuss three main questions: First, why do we need Bitcoin? The discussion typically focuses on two main issues Bitcoin addresses: inflation and censorship;Secondly, how to buy Bitcoin? We usually ask who wants to buy some Bitcoin, and then we do a small purchase together and conduct a P2P trade to demonstrate how easy it is to buy Bitcoin. Lastly, how to store Bitcoin? We introduce self-custody and show how to use hardware wallets (like Trezor), explaining the concept of the 12 words and private keys. **Keypleb**:The whole meetup usually wraps up in about an hour, after which people can continue socializing at Bitcoin House or wherever the meetup is taking place. In short, keeping the meetup simple and efficient, and ensuring a fixed location for each event, are key factors in building a successful community. **YakiHonne**: What's the major approach? Is it more technical, or do you focus on non-technical aspects, or do you cover both? **Keypleb**:Our approach includes both technical and non-technical content. Initially, our meetups were completely non-technical, just casual gatherings for people to socialize. Over time, however, we've evolved to incorporate more technical content. **Keypleb**:Out of the 31 monthly regular meetups we host, most of them have been non-technical, simply regular gatherings held at the same time and place according to our meetup guide. For example, we host the “Bitcoin for Beginners” meetup, which is designed for newcomers and takes place every second Friday of the month at 5 PM at the Bitcoin House Bali. This is entirely non-technical. Additionally, every Wednesday at Bitcoin House, we host the “My First Bitcoin” course. While the course touches on some technical aspects, such as seed phrases and backups, it’s still beginner-friendly and not too technical. The course runs for 10 weeks, and we plan to offer it in the local language at Bali University to help the local community better understand Bitcoin. **Keypleb**:On the other hand, we also offer highly technical content. We launched a new program called “Code Orange,” which is specifically designed for developers and programmers. We use the “Decoding Bitcoin” website, created by Jamal, which is a learning platform for developers. Many developer schools, like Code Orange, use this resource. Additionally, we host “Code Orange” meetups where we dive into the technical aspects of Bitcoin, such as how mining works and how to prevent single points of failure. **Keypleb**:We also organize technical workshops, such as “How to Defend Against a Five-Dollar Wrench Attack,” which is closely related to security. Recently, there have been some kidnapping incidents in Bali, and many people are concerned about their Bitcoin being stolen. To address this, we plan to hold a workshop on how to protect Bitcoin against such attacks. Additionally, we host hackathons and other high-tech events, and we just completed a very successful beginner-level hackathon. **Keypleb**:In summary, our community caters to everyone, from beginners to technical experts. For beginners, we offer easy-to-understand, non-technical content, while for experienced Bitcoiners, we provide in-depth technical material.  **YakiHonne**: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved? **Keypleb**:I have some additional advice. First, technical individuals can sign up for the “Decoding Bitcoin” course that starts on 18th March 2025 or join our “Code Orange” program and participate in the end-of-year hackathon. If they are technically proficient, this will be a great opportunity. “Decoding Bitcoin” is great for beginners, but it’s also useful for technical individuals. If someone is very skilled, they can start contributing code right away. If they find the course too easy, they can skip it and dive directly into more advanced projects. Additionally, Bitshala and Chaincode Labs offer advanced courses, which more technically advanced individuals can choose to pursue.  **Keypleb**:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash. **YakiHonne**: I’d like to move on to the next question: How do you see Bitcoin communities evolving as technology progresses, particularly in areas like scalability, privacy, and adaptability to other systems? Keypleb:I believe the Bitcoin community will continue to evolve, and it has already made incredible progress. Two and a half years ago, we started alone in Bali, with just ourselves. We began in the official phase and have had numerous conversations throughout the year. For example, we are now starting a Bitcoin club at a university in Bali; we just need to find a passionate, driven “Bitcoin maximalist,” and the Bitcoin club will begin. Like what our friends did in Banyuwangi, Indonesia, these clubs could eventually evolve into Bitcoin houses. **Keypleb**:Regarding privacy and scalability, the community is making strides. We’re big fans of Fedi, which builds on top of the Fedimint protocol and uses e-cash to scale Bitcoin while improving privacy. Fedi low fees and high privacy potential give Bitcoin great opportunities in this area. **Keypleb**:As for Bitcoin's compatibility with fiat systems, although Bitcoin payments are illegal in some countries like Indonesia, smart developers across Southeast Asia are working on legal solutions. For example, there's a website called Pleb QR that works in Thailand, allowing you to pay in fiat via the Lightning Network. Koral is another app specifically for Indonesia. These kinds of testing products already exist and are physically possible, but we’re just waiting on regulations. My influential friends are actively lobbying the government for adoption. **Keypleb**:In summary, privacy, scalability, and compatibility with fiat systems are all works in progress, and they will continue to evolve positively. There will be more meetups, more wallet downloads, and more adoption—there’s no doubt about that. **YakiHonne**: You mentioned the concept of cross-country issues, so I have one last question: How is the government’s stance on Bitcoin? Is the political climate supportive or against Bitcoin? How do you see the government's approach to Bitcoin in your community or environment? **Keypleb**:This reminds me of a person, Jeff Booth, who once said, “We are them, the government is made up of us.” In Indonesia, many politicians actually support Bitcoin, and many of them mine Bitcoin themselves. When money is involved, the incentive is strong, and politicians naturally like to make more money. As a result, Indonesia has a large Bitcoin mining scene. However, overall, the Indonesian government is against Bitcoin, as seen in their ban on Bitcoin payments. The 2011 currency law states that any currency other than the Indonesian Rupiah (IDR) cannot be used, and violators can face up to one year in prison or a fine. This means you cannot pay with US dollars, lira, euros, pesos or pounds. **Keypleb**:This shows that the government’s legal system is somewhat fragile. It’s understandable that the government is concerned about disruptive technologies like Bitcoin, especially with such a fragile fiat system. Indonesia has also seen many arrests. In 2016, Bank Indonesia issued a letter announcing a crackdown on cryptocurrency payments. Those involved in paying in Bitcoin had their funds seized, and the police cooperated in shutting down businesses accepting Bitcoin payments in the cities. While this isn't very friendly, it does highlight the fragility of the existing system. We also believe that a new executive order may be introduced in the future, similar to when President Roosevelt in 1933 ordered Americans to hand over all their gold with his Executive Order 6102. If it happened before, it could happen again. **Keypleb**:Therefore, we predict that Bitcoin custody could become a legal issue, which is one of the reasons we blur the faces of participants at every meetup. We need to protect the community from any potential risks. But overall, we remain optimistic. Despite the government ban, the ideology of Bitcoin is unstoppable, and its spread cannot be stopped. So, we are very optimistic about the future. **YakiHonne**: I think almost every government around the world, even in Africa, faces similar issues with Bitcoin. Some governments might want Bitcoin but hesitate to openly accept it due to the fear of it undermining the traditional financial system, which, of course, could eventually happen. But hopefully, as the new generation comes into power, we'll see more Bitcoin-friendly governments. So, thank you so much for sharing your insights and advice. I really appreciate your time and the valuable input you've provided. **Keypleb**:I'm really glad this conversation enlightened me. I enjoyed it a lot, and it made me reflect on how much work we're doing and how valuable it is. There are a lot of problems out there, with censorship being the biggest one, followed by inflation, which is also a major issue depending on the region. But Bitcoin is open, the community is growing, and people are fighting against censorship and internet shutdowns in places like Indonesia and beyond. The movement is definitely growing. So, I'm very happy to be here and have this chat. Thanks again. Bitcoin Indonesia nostr: nostr:npub1y4qd2zhtn05gnsaaq5xfejzfk4a32638tx6gpp9g8k6e42g9d66qaxhcr3 Keypleb nostr: nostr:npub190trvg63e6tyqlwlj6lccqpftx76lckj25c006vwx3dzvdl88yxs2nyqdx @ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice. A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases. Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy. Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest. Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice. A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases. Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy. Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest. Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever. @ 7d33ba57:1b82db35
2025-04-01 09:17:32Šibenik is a charming coastal town in Dalmatia, known for its stunning medieval architecture, UNESCO-listed cathedral, and scenic Adriatic coastline. Unlike many other Croatian coastal cities, Šibenik was founded by Croats (not Romans or Venetians), giving it a unique identity. It’s also the perfect gateway to Krka National Park and the Kornati Islands.  ## **🏰 Top Things to See & Do in Šibenik** ### **1️⃣ St. James Cathedral (UNESCO) ⛪** - **One of Croatia’s most impressive churches**, built entirely of **stone**. - Features **intricate carvings** of **71 sculpted faces**, believed to be real Šibenik residents from the 15th century. - A masterpiece blending **Gothic and Renaissance styles**, recognized as a **UNESCO World Heritage Site**. ### **2️⃣ Explore the Medieval Old Town 🏡** - Wander through **narrow, stone-paved streets** filled with history. - Discover hidden squares, old churches, and charming cafés. - Stop by the **Four Wells Square**, where locals once gathered for water.  ### **3️⃣ Climb to St. Michael’s Fortress 🏰** - Offers **breathtaking panoramic views** over Šibenik and the Adriatic. - Hosts **concerts & cultural events** in a unique open-air setting. - One of Šibenik’s **four medieval fortresses**, well-preserved and full of history. ### **4️⃣ Visit Barone & St. John’s Fortresses 🏗️** - **Barone Fortress** – Features an **interactive museum** and stunning **sunset views**. - **St. John’s Fortress** – Famous for being a filming location for **Game of Thrones**. ### **5️⃣ Day Trip to Krka National Park 🌿💦** - Just **15 minutes away**, Krka is home to **stunning waterfalls** and **lush greenery**. - Walk the wooden pathways to **Skradinski Buk**, the park’s **largest waterfall**. - **Boat tours** take you to **Visovac Island**, home to a historic monastery.  ### **6️⃣ Boat Trip to Kornati Islands 🏝️⛵** - A group of **89 islands**, known as the **"nautical paradise"** of Croatia. - Ideal for **sailing, snorkeling, and exploring unspoiled nature**. - Book a **boat tour** from Šibenik’s harbor for a day of adventure. ### **7️⃣ Relax at Banj Beach 🏖️** - A **city beach with crystal-clear waters**, just a **short walk from the Old Town**. - Offers stunning **views of Šibenik’s skyline and fortresses**. - Great for swimming and sunbathing. ### **8️⃣ Enjoy Fresh Dalmatian Cuisine 🍽️** - Try **peka** – a traditional dish of slow-cooked meat and vegetables. - **Šibenik’s seafood** is top-notch – grilled fish, octopus salad, and black risotto. - Pair your meal with local **Babić wine**, produced in nearby vineyards.  ## **🚗 How to Get to Šibenik** ✈️ **By Air:** Nearest airports: - **Split Airport (SPU)** – **45 min drive (60 km)** - **Zadar Airport (ZAD)** – **50 min drive (70 km)** 🚘 **By Car:** - **From Split:** ~1 hour (90 km) - **From Zadar:** ~1 hour (85 km) 🚌 **By Bus:** Direct buses from **Split, Zadar, and Zagreb**. ⛵ **By Boat:** Ferries connect Šibenik to nearby islands like **Zlarin and Prvić**.  ## **💡 Tips for Visiting Šibenik** ✅ **Best time to visit?** **May–September** for warm weather & outdoor festivals ☀️ ✅ **Wear comfy shoes** – The Old Town’s stone streets can be steep & slippery 👟 ✅ **Plan Krka trips early** – It gets busy, especially in summer 🚣 ✅ **Try local olive oil & wine** – Some of Croatia’s best olive oils & wines come from Šibenik’s region 🍷🫒 ✅ **Stay for sunset** – The views from St. Michael’s Fortress are unforgettable 🌅 
@ 7d33ba57:1b82db35
2025-04-01 09:17:32Šibenik is a charming coastal town in Dalmatia, known for its stunning medieval architecture, UNESCO-listed cathedral, and scenic Adriatic coastline. Unlike many other Croatian coastal cities, Šibenik was founded by Croats (not Romans or Venetians), giving it a unique identity. It’s also the perfect gateway to Krka National Park and the Kornati Islands.  ## **🏰 Top Things to See & Do in Šibenik** ### **1️⃣ St. James Cathedral (UNESCO) ⛪** - **One of Croatia’s most impressive churches**, built entirely of **stone**. - Features **intricate carvings** of **71 sculpted faces**, believed to be real Šibenik residents from the 15th century. - A masterpiece blending **Gothic and Renaissance styles**, recognized as a **UNESCO World Heritage Site**. ### **2️⃣ Explore the Medieval Old Town 🏡** - Wander through **narrow, stone-paved streets** filled with history. - Discover hidden squares, old churches, and charming cafés. - Stop by the **Four Wells Square**, where locals once gathered for water.  ### **3️⃣ Climb to St. Michael’s Fortress 🏰** - Offers **breathtaking panoramic views** over Šibenik and the Adriatic. - Hosts **concerts & cultural events** in a unique open-air setting. - One of Šibenik’s **four medieval fortresses**, well-preserved and full of history. ### **4️⃣ Visit Barone & St. John’s Fortresses 🏗️** - **Barone Fortress** – Features an **interactive museum** and stunning **sunset views**. - **St. John’s Fortress** – Famous for being a filming location for **Game of Thrones**. ### **5️⃣ Day Trip to Krka National Park 🌿💦** - Just **15 minutes away**, Krka is home to **stunning waterfalls** and **lush greenery**. - Walk the wooden pathways to **Skradinski Buk**, the park’s **largest waterfall**. - **Boat tours** take you to **Visovac Island**, home to a historic monastery.  ### **6️⃣ Boat Trip to Kornati Islands 🏝️⛵** - A group of **89 islands**, known as the **"nautical paradise"** of Croatia. - Ideal for **sailing, snorkeling, and exploring unspoiled nature**. - Book a **boat tour** from Šibenik’s harbor for a day of adventure. ### **7️⃣ Relax at Banj Beach 🏖️** - A **city beach with crystal-clear waters**, just a **short walk from the Old Town**. - Offers stunning **views of Šibenik’s skyline and fortresses**. - Great for swimming and sunbathing. ### **8️⃣ Enjoy Fresh Dalmatian Cuisine 🍽️** - Try **peka** – a traditional dish of slow-cooked meat and vegetables. - **Šibenik’s seafood** is top-notch – grilled fish, octopus salad, and black risotto. - Pair your meal with local **Babić wine**, produced in nearby vineyards.  ## **🚗 How to Get to Šibenik** ✈️ **By Air:** Nearest airports: - **Split Airport (SPU)** – **45 min drive (60 km)** - **Zadar Airport (ZAD)** – **50 min drive (70 km)** 🚘 **By Car:** - **From Split:** ~1 hour (90 km) - **From Zadar:** ~1 hour (85 km) 🚌 **By Bus:** Direct buses from **Split, Zadar, and Zagreb**. ⛵ **By Boat:** Ferries connect Šibenik to nearby islands like **Zlarin and Prvić**.  ## **💡 Tips for Visiting Šibenik** ✅ **Best time to visit?** **May–September** for warm weather & outdoor festivals ☀️ ✅ **Wear comfy shoes** – The Old Town’s stone streets can be steep & slippery 👟 ✅ **Plan Krka trips early** – It gets busy, especially in summer 🚣 ✅ **Try local olive oil & wine** – Some of Croatia’s best olive oils & wines come from Šibenik’s region 🍷🫒 ✅ **Stay for sunset** – The views from St. Michael’s Fortress are unforgettable 🌅  @ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits. **Small Wins** Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it. **Ego is Volatile** Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic. **Simplicity** There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life. **The Big Picture** Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits. **Small Wins** Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it. **Ego is Volatile** Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic. **Simplicity** There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life. **The Big Picture** Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡 @ 7d94dfe7:49219865
2025-04-01 10:31:12Short answer: Yes
@ 7d94dfe7:49219865
2025-04-01 10:31:12Short answer: Yes @ 6389be64:ef439d32
2025-02-27 21:32:12GA, plebs. The latest episode of Bitcoin And is out, and, as always, the chicanery is running rampant. Let’s break down the biggest topics I covered, and if you want the full, unfiltered rant, make sure to listen to the episode linked below. ## House Democrats’ MEME Act: A Bad Joke? House Democrats are proposing a bill to ban presidential meme coins, clearly aimed at Trump’s and Melania’s ill-advised token launches. While grifters launching meme coins is bad, this bill is just as ridiculous. If this legislation moves forward, expect a retaliatory strike exposing how politicians like Pelosi and Warren mysteriously amassed their fortunes. Will it pass? Doubtful. But it’s another sign of the government’s obsession with regulating everything except itself. ## Senate Banking’s First Digital Asset Hearing: The Real Target Is You Cynthia Lummis chaired the first digital asset hearing, and—surprise!—it was all about control. The discussion centered on stablecoins, AML, and KYC regulations, with witnesses suggesting Orwellian measures like freezing stablecoin transactions unless pre-approved by authorities. What was barely mentioned? Bitcoin. They want full oversight of stablecoins, which is really about controlling financial freedom. Expect more nonsense targeting self-custody wallets under the guise of stopping “bad actors.” ## Bank of America and PayPal Want In on Stablecoins Bank of America’s CEO openly stated they’ll launch a stablecoin as soon as regulation allows. Meanwhile, PayPal’s CEO paid for a hat using Bitcoin—not their own stablecoin, Pi USD. Why wouldn’t he use his own product? Maybe he knows stablecoins aren’t what they’re hyped up to be. Either way, the legacy financial system is gearing up to flood the market with stablecoins, not because they love crypto, but because it’s a tool to extend U.S. dollar dominance. ## MetaPlanet Buys the Dip Japan’s MetaPlanet issued $13.4M in bonds to buy more Bitcoin, proving once again that institutions see the writing on the wall. Unlike U.S. regulators who obsess over stablecoins, some companies are actually stacking sats. ## UK Expands Crypto Seizure Powers Across the pond, the UK government is pushing legislation to make it easier to seize and destroy crypto linked to criminal activity. While they frame it as going after the bad guys, it’s another move toward centralized control and financial surveillance. ## Bitcoin Tools & Tech: Arc, SatoChip, and Nunchuk Some bullish Bitcoin developments: ARC v0.5 is making Bitcoin’s second layer more efficient, SatoChip now supports Taproot and Nostr, and Nunchuk launched a group wallet with chat, making multisig collaboration easier. ## The Bottom Line The state is coming for financial privacy and control, and stablecoins are their weapon of choice. Bitcoiners need to stay focused, keep their coins in self-custody, and build out parallel systems. Expect more regulatory attacks, but don’t let them distract you—just keep stacking and transacting in ways they can’t control. **🎧 Listen to the full episode here: [https://fountain.fm/episode/PYITCo18AJnsEkKLz2Ks](Fountain.fm)** **💰 Support the show by boosting sats on Podcasting 2.0!** and I will see you on the other side.
@ 6389be64:ef439d32
2025-02-27 21:32:12GA, plebs. The latest episode of Bitcoin And is out, and, as always, the chicanery is running rampant. Let’s break down the biggest topics I covered, and if you want the full, unfiltered rant, make sure to listen to the episode linked below. ## House Democrats’ MEME Act: A Bad Joke? House Democrats are proposing a bill to ban presidential meme coins, clearly aimed at Trump’s and Melania’s ill-advised token launches. While grifters launching meme coins is bad, this bill is just as ridiculous. If this legislation moves forward, expect a retaliatory strike exposing how politicians like Pelosi and Warren mysteriously amassed their fortunes. Will it pass? Doubtful. But it’s another sign of the government’s obsession with regulating everything except itself. ## Senate Banking’s First Digital Asset Hearing: The Real Target Is You Cynthia Lummis chaired the first digital asset hearing, and—surprise!—it was all about control. The discussion centered on stablecoins, AML, and KYC regulations, with witnesses suggesting Orwellian measures like freezing stablecoin transactions unless pre-approved by authorities. What was barely mentioned? Bitcoin. They want full oversight of stablecoins, which is really about controlling financial freedom. Expect more nonsense targeting self-custody wallets under the guise of stopping “bad actors.” ## Bank of America and PayPal Want In on Stablecoins Bank of America’s CEO openly stated they’ll launch a stablecoin as soon as regulation allows. Meanwhile, PayPal’s CEO paid for a hat using Bitcoin—not their own stablecoin, Pi USD. Why wouldn’t he use his own product? Maybe he knows stablecoins aren’t what they’re hyped up to be. Either way, the legacy financial system is gearing up to flood the market with stablecoins, not because they love crypto, but because it’s a tool to extend U.S. dollar dominance. ## MetaPlanet Buys the Dip Japan’s MetaPlanet issued $13.4M in bonds to buy more Bitcoin, proving once again that institutions see the writing on the wall. Unlike U.S. regulators who obsess over stablecoins, some companies are actually stacking sats. ## UK Expands Crypto Seizure Powers Across the pond, the UK government is pushing legislation to make it easier to seize and destroy crypto linked to criminal activity. While they frame it as going after the bad guys, it’s another move toward centralized control and financial surveillance. ## Bitcoin Tools & Tech: Arc, SatoChip, and Nunchuk Some bullish Bitcoin developments: ARC v0.5 is making Bitcoin’s second layer more efficient, SatoChip now supports Taproot and Nostr, and Nunchuk launched a group wallet with chat, making multisig collaboration easier. ## The Bottom Line The state is coming for financial privacy and control, and stablecoins are their weapon of choice. Bitcoiners need to stay focused, keep their coins in self-custody, and build out parallel systems. Expect more regulatory attacks, but don’t let them distract you—just keep stacking and transacting in ways they can’t control. **🎧 Listen to the full episode here: [https://fountain.fm/episode/PYITCo18AJnsEkKLz2Ks](Fountain.fm)** **💰 Support the show by boosting sats on Podcasting 2.0!** and I will see you on the other side. @ e373ca41:b82abcc5
2025-04-01 08:44:15*** *This article first appeared in German at* ***[Freischwebende Intelligenz.](https://www.freischwebende-intelligenz.org/p/an-der-zeitmauer-der-entblindung)*** *You can find all the articles by Free-floating Intelligence in English* ***[here](https://pareto.space/u/ashoka@pareto.space)*** *– subscribe now, to get the articles by e-mail!* *This article has been written with the* ***[Pareto client](https://pareto.space/read).*** *** > “The real partner of the earth is not the mind with its titanic plans, but the spirit as a cosmic power. In all considerations of contemporary events, therefore, the more or less expressed hope plays a role that higher spiritual forces will restrain the mighty movement and beneficially take possession of it.” – Ernst Jünger, An der Zeitmauer It is characteristic of a time of crisis that upheavals take a long time to occur, but then happen suddenly and simultaneously. We are currently experiencing huge movements on all levels - material, mental and spiritual. What is happening looks less like a changeover, a shift in coordinates or a correction, and more like an inversion of the world to the other, previously suppressed side, a Copernican turn of power. ### Inversion in fast motion We are experiencing the offshoots of this on a daily basis, almost every minute in a carousel of cataclysmic events via the new event ticker “X”. * Selenski, who was initially passed around by the US elite as the darling of the world stage, was virtually chased from court after heated exchanges over realpolitik interests (assistance vs. natural resources). The world's population watched in amazement at this public humiliation ritual. * Money, which always seemed to be there when it was needed, is suddenly seen as a scarce commodity. In the USA, the books are being audited, zombie civil servants are being asked by email to submit weekly balance sheets, and next it will be the turn of the gold in Fort Knox. This is where the substance of trust of the still-ruling superpower is at stake. How much of the US construct is real, what is a show? * Investigative zeal is spreading: Suddenly people are interested in vaccination damage and pharmaceutical studies, the moon landing, 9/11, aliens, the background to JFK's assassination – and whether Hitler fled to Argentina to become Shift-Führer at Volkswagen.  \ Every change of power involves recalibrating the truth, sometimes by ditching the old elite. Promises no longer count, only deeds. In the Epstein case, public trust and revenge of a new elite on the old one culminate, including public shaming and reckoning. Ritual humiliation is joined by sacrifice. Will it be a real one or just a staged one? \ Only Bitcoin seems to be following the normal program of every cycle amid all the turmoil: Massive rises, expected setbacks, and otherwise the usual crypto mix of hacks (Bybit), scams (HawkTuah & Co.), and celebrity memecoins from Trump to Alice. \ The dissolution of the old order creates new voids and problems of definition. What is NATO without the USA? What is Germany? What is the EU? Old personnel are leaving, new ones are not yet in sight. A metaphysical interregnum that manifests itself in the institutional. At the same time, the Pope was practically dying, just like his institution. ") ### The signs on the wall We are at a new wall of time. Ernst Jünger used this term to describe a concentration of spiritual and cosmic forces that have the potential to lift mankind to a new level of development. For him, revolutions were foreshadowed in the stars. In the French Revolution, the people rose above the nobility and clergy, and with the atomic age at the latest, a new elite with a button and a suitcase took over the world. Since then, the fate of the earth, its destruction or its continued existence have been in the hands of our species. With the new age of human transformation, be it genetic, cybernetic or neuronal, the question has recently arisen as to whether mankind will first destroy itself from within before it succeeds with the earth. Admittedly, this does not sound like a golden age for mankind. Our time seems to consist more of archaic (warlike) elements and the new siliceous elements of the artificial world. The permanent and static is once again evaporating and is therefore neither permanent nor stable. At the same time, networking and data collection are creating a new predictability of the individual. Jünger: “The most gruesome prospect is that of technocracy, a controlling rule exercised by mutilated and mutilating spirits.” *** **Do you want to get the articles from Free-floating Intelligence by Mail? Subscribe** **[here.](https://pareto.space/u/ashoka@pareto.space)** *** In “Generation Chillstand”, I dealt with the decoupling of the new from the old on a generational level. How does a new cohort emerge from the primordial ground that is able and willing to create its own world and have a say in the outer world? * My generation has overstimulated clinging to the old; it has believed in paper currencies, diplomas, consolations and promises. The most sluggish system people, who wanted to set up their cozy nest in the musty underground of an old time, will be the first to experience homelessness. * Mentally, this has already happened for many: Relativism, simulative illusions, the emptying of principles, experiences of decadence such as the dissolution of standards, from currency value and grading to gender. Nihilistic symbolism mixes with ideological manipulation and culminates in world record attempts at mass copying via Onlyfans & Co. Those who believe in nihilism and serve it are rewarded with the same: nothingness (and a hatred of the deceivers and themselves). * Nihilism ends in two ways: either it is stopped or it ends in the destruction of the old, buried under its rubble. ### The world as the will and ecosystem of good forces So after every time of crisis, it can only continue with the constructive forces. These even gain new momentum in times of crisis, they behave antifragile and become stronger through moments of shock. Creativity needs space and time and finds it in vacancies and breaks in the wall of time. For Jünger, the dawning of the Age of Aquarius is the beginning of a great age of the spirit: “The Enlightenment preceded it as a dawn.” Is Jünger right here? Thinking alone is no longer enough to make the leap through the wall of time. Computers have long since outstripped humans in this respect. Mind must mean more here than gigabytes and brains. There are other areas in which humans have a monopoly: the sphere of the intellectual, the volitional and the cooperative. *** ADVERTISEMENT: *Looking for the easiest way to buy Bitcoin and store it yourself? The **[Relai app](https://relai.app/de/?af_xp=custom\&source_caller=ui\&pid=INFLUENCER\&is_retargeting=true\&af_click_lookback=7d\&shortlink=eo5zpzew\&af_channel=branded_url\&af_inactivity_window=30d\&c=Milosz%20Matuszek)** is the No. 1 crypto start-up and No. 2 of all fintech start-ups in Switzerland. **[Here you can buy Bitcoin](https://relai.app/de/?af_xp=custom\&source_caller=ui\&pid=INFLUENCER\&is_retargeting=true\&af_click_lookback=7d\&shortlink=eo5zpzew\&af_channel=branded_url\&af_inactivity_window=30d\&c=Milosz%20Matuszek)** in just a few steps and also set up savings plans. Nobody has access to your Bitcoin except you. With the referral code MILOSZ you save on fees (no financial advice). Disclaimer due to regulatory issues: The services of the Relai App are hereby only recommended to inhabitants of Switzerland or Italy.*  *Need more security? The **[Trezor wallets](https://trezor.io/trezor-safe-5-bitcoin-only?transaction_id=102e192a206d1585e56a2fddef6d83\&offer_id=238\&affiliate_id=35234)** are recommended and easy to use, others are available in the **[store](https://trezor.io/?transaction_id=102bc85bdca2733287749c7f879ebd\&offer_id=133\&affiliate_id=35234)**. Need more advice? Book an **[introductory meeting](https://trezor.io/trezor-expert-session?transaction_id=1020e18dad0aa4b1186289fd22e90f\&offer_id=241\&affiliate_id=35234)** with a wallet expert.* *** Machines have no substance of their own at their core, they are not capable of creativity, only of reorganization. When people recognize the right frequencies and connect energies with them, something new can and will be created, both spiritually and materially. This is the wall of time through which we must pass. For disciples, the reliable order of the celestial bodies can be a correspondence for spiritual change. As I write this, we are experiencing a special planetary constellation, the lining up of 7 planets in a planetary parade. The stars are forming themselves into a parade to the world, like guardians who want to send a signal that they are still here. What do they want to tell us? “Line up”? “Form a constellation”? The signs on the wall of the Time Wall are the same for everyone. It says “Apocalypse” right there. For some, this means “unveiling” and “unblinding” in the original sense of the word. For the others: Downfall. Which meaning do you choose? *** # One last thing Our funds are coming to an end. If you would like to support us: We have started a [crowdfunding on Geyser](https://geyser.fund/project/pareto), where you can help us with Bitcoin/Lightning donations.  For traditional donations, you can find our bank account on our **[landingpage.](https://pareto.space/en)** *** ***Join the marketplace of ideas!** We are building a publishing ecosystem on Nostr for citizen-journalism, starting with a client for blogging and newsletter distribution. Sound money and sound information should finally be in the hands of the people, right? Want to learn more about the [Pareto Project](https://pareto.space/en)? Zap me, if you want to contribute (all Zaps go to the project).* *Are you a publication or journalist and want to be part of it, test us, migrate your content to Nostr? Write to **<team@pareto.space>*** **Not yet on** **[Nostr](https://nostr.com/)** **and want the full experience?** Easy onboarding via **[Start.](https://start.njump.me/)**
@ e373ca41:b82abcc5
2025-04-01 08:44:15*** *This article first appeared in German at* ***[Freischwebende Intelligenz.](https://www.freischwebende-intelligenz.org/p/an-der-zeitmauer-der-entblindung)*** *You can find all the articles by Free-floating Intelligence in English* ***[here](https://pareto.space/u/ashoka@pareto.space)*** *– subscribe now, to get the articles by e-mail!* *This article has been written with the* ***[Pareto client](https://pareto.space/read).*** *** > “The real partner of the earth is not the mind with its titanic plans, but the spirit as a cosmic power. In all considerations of contemporary events, therefore, the more or less expressed hope plays a role that higher spiritual forces will restrain the mighty movement and beneficially take possession of it.” – Ernst Jünger, An der Zeitmauer It is characteristic of a time of crisis that upheavals take a long time to occur, but then happen suddenly and simultaneously. We are currently experiencing huge movements on all levels - material, mental and spiritual. What is happening looks less like a changeover, a shift in coordinates or a correction, and more like an inversion of the world to the other, previously suppressed side, a Copernican turn of power. ### Inversion in fast motion We are experiencing the offshoots of this on a daily basis, almost every minute in a carousel of cataclysmic events via the new event ticker “X”. * Selenski, who was initially passed around by the US elite as the darling of the world stage, was virtually chased from court after heated exchanges over realpolitik interests (assistance vs. natural resources). The world's population watched in amazement at this public humiliation ritual. * Money, which always seemed to be there when it was needed, is suddenly seen as a scarce commodity. In the USA, the books are being audited, zombie civil servants are being asked by email to submit weekly balance sheets, and next it will be the turn of the gold in Fort Knox. This is where the substance of trust of the still-ruling superpower is at stake. How much of the US construct is real, what is a show? * Investigative zeal is spreading: Suddenly people are interested in vaccination damage and pharmaceutical studies, the moon landing, 9/11, aliens, the background to JFK's assassination – and whether Hitler fled to Argentina to become Shift-Führer at Volkswagen.  \ Every change of power involves recalibrating the truth, sometimes by ditching the old elite. Promises no longer count, only deeds. In the Epstein case, public trust and revenge of a new elite on the old one culminate, including public shaming and reckoning. Ritual humiliation is joined by sacrifice. Will it be a real one or just a staged one? \ Only Bitcoin seems to be following the normal program of every cycle amid all the turmoil: Massive rises, expected setbacks, and otherwise the usual crypto mix of hacks (Bybit), scams (HawkTuah & Co.), and celebrity memecoins from Trump to Alice. \ The dissolution of the old order creates new voids and problems of definition. What is NATO without the USA? What is Germany? What is the EU? Old personnel are leaving, new ones are not yet in sight. A metaphysical interregnum that manifests itself in the institutional. At the same time, the Pope was practically dying, just like his institution. ") ### The signs on the wall We are at a new wall of time. Ernst Jünger used this term to describe a concentration of spiritual and cosmic forces that have the potential to lift mankind to a new level of development. For him, revolutions were foreshadowed in the stars. In the French Revolution, the people rose above the nobility and clergy, and with the atomic age at the latest, a new elite with a button and a suitcase took over the world. Since then, the fate of the earth, its destruction or its continued existence have been in the hands of our species. With the new age of human transformation, be it genetic, cybernetic or neuronal, the question has recently arisen as to whether mankind will first destroy itself from within before it succeeds with the earth. Admittedly, this does not sound like a golden age for mankind. Our time seems to consist more of archaic (warlike) elements and the new siliceous elements of the artificial world. The permanent and static is once again evaporating and is therefore neither permanent nor stable. At the same time, networking and data collection are creating a new predictability of the individual. Jünger: “The most gruesome prospect is that of technocracy, a controlling rule exercised by mutilated and mutilating spirits.” *** **Do you want to get the articles from Free-floating Intelligence by Mail? Subscribe** **[here.](https://pareto.space/u/ashoka@pareto.space)** *** In “Generation Chillstand”, I dealt with the decoupling of the new from the old on a generational level. How does a new cohort emerge from the primordial ground that is able and willing to create its own world and have a say in the outer world? * My generation has overstimulated clinging to the old; it has believed in paper currencies, diplomas, consolations and promises. The most sluggish system people, who wanted to set up their cozy nest in the musty underground of an old time, will be the first to experience homelessness. * Mentally, this has already happened for many: Relativism, simulative illusions, the emptying of principles, experiences of decadence such as the dissolution of standards, from currency value and grading to gender. Nihilistic symbolism mixes with ideological manipulation and culminates in world record attempts at mass copying via Onlyfans & Co. Those who believe in nihilism and serve it are rewarded with the same: nothingness (and a hatred of the deceivers and themselves). * Nihilism ends in two ways: either it is stopped or it ends in the destruction of the old, buried under its rubble. ### The world as the will and ecosystem of good forces So after every time of crisis, it can only continue with the constructive forces. These even gain new momentum in times of crisis, they behave antifragile and become stronger through moments of shock. Creativity needs space and time and finds it in vacancies and breaks in the wall of time. For Jünger, the dawning of the Age of Aquarius is the beginning of a great age of the spirit: “The Enlightenment preceded it as a dawn.” Is Jünger right here? Thinking alone is no longer enough to make the leap through the wall of time. Computers have long since outstripped humans in this respect. Mind must mean more here than gigabytes and brains. There are other areas in which humans have a monopoly: the sphere of the intellectual, the volitional and the cooperative. *** ADVERTISEMENT: *Looking for the easiest way to buy Bitcoin and store it yourself? The **[Relai app](https://relai.app/de/?af_xp=custom\&source_caller=ui\&pid=INFLUENCER\&is_retargeting=true\&af_click_lookback=7d\&shortlink=eo5zpzew\&af_channel=branded_url\&af_inactivity_window=30d\&c=Milosz%20Matuszek)** is the No. 1 crypto start-up and No. 2 of all fintech start-ups in Switzerland. **[Here you can buy Bitcoin](https://relai.app/de/?af_xp=custom\&source_caller=ui\&pid=INFLUENCER\&is_retargeting=true\&af_click_lookback=7d\&shortlink=eo5zpzew\&af_channel=branded_url\&af_inactivity_window=30d\&c=Milosz%20Matuszek)** in just a few steps and also set up savings plans. Nobody has access to your Bitcoin except you. With the referral code MILOSZ you save on fees (no financial advice). Disclaimer due to regulatory issues: The services of the Relai App are hereby only recommended to inhabitants of Switzerland or Italy.*  *Need more security? The **[Trezor wallets](https://trezor.io/trezor-safe-5-bitcoin-only?transaction_id=102e192a206d1585e56a2fddef6d83\&offer_id=238\&affiliate_id=35234)** are recommended and easy to use, others are available in the **[store](https://trezor.io/?transaction_id=102bc85bdca2733287749c7f879ebd\&offer_id=133\&affiliate_id=35234)**. Need more advice? Book an **[introductory meeting](https://trezor.io/trezor-expert-session?transaction_id=1020e18dad0aa4b1186289fd22e90f\&offer_id=241\&affiliate_id=35234)** with a wallet expert.* *** Machines have no substance of their own at their core, they are not capable of creativity, only of reorganization. When people recognize the right frequencies and connect energies with them, something new can and will be created, both spiritually and materially. This is the wall of time through which we must pass. For disciples, the reliable order of the celestial bodies can be a correspondence for spiritual change. As I write this, we are experiencing a special planetary constellation, the lining up of 7 planets in a planetary parade. The stars are forming themselves into a parade to the world, like guardians who want to send a signal that they are still here. What do they want to tell us? “Line up”? “Form a constellation”? The signs on the wall of the Time Wall are the same for everyone. It says “Apocalypse” right there. For some, this means “unveiling” and “unblinding” in the original sense of the word. For the others: Downfall. Which meaning do you choose? *** # One last thing Our funds are coming to an end. If you would like to support us: We have started a [crowdfunding on Geyser](https://geyser.fund/project/pareto), where you can help us with Bitcoin/Lightning donations.  For traditional donations, you can find our bank account on our **[landingpage.](https://pareto.space/en)** *** ***Join the marketplace of ideas!** We are building a publishing ecosystem on Nostr for citizen-journalism, starting with a client for blogging and newsletter distribution. Sound money and sound information should finally be in the hands of the people, right? Want to learn more about the [Pareto Project](https://pareto.space/en)? Zap me, if you want to contribute (all Zaps go to the project).* *Are you a publication or journalist and want to be part of it, test us, migrate your content to Nostr? Write to **<team@pareto.space>*** **Not yet on** **[Nostr](https://nostr.com/)** **and want the full experience?** Easy onboarding via **[Start.](https://start.njump.me/)** @ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from *The Mandibles: A Family, 2029–2047* by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes. ### Part One: 2029–2032 - **2029 (Early Year)**\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor. - **2029 (Mid-Year: The Great Renunciation)**\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive. - **2029 (Late Year)**\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant. - **2030–2031**\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness. - **2032**\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured. ### Time Jump: 2032–2047 - Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies. ### Part Two: 2047 - **2047 (Early Year)**\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum. - **2047 (Mid-Year)**\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency. - **2047 (Late Year)**\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society. ### Key Differences - **Currency Dynamics**: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control. - **Government Power**: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities. - **Societal Outcome**: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots. This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
@ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from *The Mandibles: A Family, 2029–2047* by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes. ### Part One: 2029–2032 - **2029 (Early Year)**\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor. - **2029 (Mid-Year: The Great Renunciation)**\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive. - **2029 (Late Year)**\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant. - **2030–2031**\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness. - **2032**\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured. ### Time Jump: 2032–2047 - Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies. ### Part Two: 2047 - **2047 (Early Year)**\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum. - **2047 (Mid-Year)**\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency. - **2047 (Late Year)**\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society. ### Key Differences - **Currency Dynamics**: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control. - **Government Power**: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities. - **Societal Outcome**: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots. This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory. @ da0b9bc3:4e30a4a9
2025-04-01 06:06:42Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/930903
@ da0b9bc3:4e30a4a9
2025-04-01 06:06:42Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/930903 @ 2b24a1fa:17750f64
2025-04-01 08:18:00„Die Mauer muss weg!“, wurde vor 35 Jahre skandiert. Jetzt muss wieder eine Mauer her: Die Brandmauer gegen rechts. Eine Gesinnungs-Mauer, eine Weltanschauungs-Mauer, eine Werte-Mauer. <https://soundcloud.com/radiomuenchen/die-neue-deutsche-angst-von-birgit-assel> Der Verlauf ist allerdings noch nicht ganz klar. Verläuft sie zwischen Menschen oder vielleicht sogar durch die Menschen selbst? Denn was bedeutet diese Brandmauer aus psychologischer, genauer aus traumatherapeutischer Sicht? Handelt es sich bei ihr nicht vielmehr um einen vehement zur Anwendung kommenden Abgrenzungsmechanismus gegen die eigenen Schattenanteile? Nicht nur, aber gerade in Deutschland tragen viele Menschen einen Rucksack verdrängter Gefühle und Schatten: den Schrecken zweier Weltkriege, Verdrängung, Armut, Flucht, schwarze Pädagogik und den Mangel durch emotional oder real abwesende Eltern – all das wirkt bis ins Heute nach. Und es vielleicht ist es ein Puzzelstein in der Erklärung so einiger hysteriegeschwängerter Phänome der Jetztzeit. Die Traumatherapeutin Birgit Assel hat sich dieser Analyse angenommen. Hören Sie hierzu ihren Text „Die neue deutsche Angst“, der zunächst im Manova Magazin erschienen war. [www.manova.news/artikel/die-neue-deutsche-angst](https://www.manova.news/artikel/die-neue-deutsche-angst "https://www.manova.news/artikel/die-neue-deutsche-angst") Sprecherin: Sabrina Khalil 
@ 2b24a1fa:17750f64
2025-04-01 08:18:00„Die Mauer muss weg!“, wurde vor 35 Jahre skandiert. Jetzt muss wieder eine Mauer her: Die Brandmauer gegen rechts. Eine Gesinnungs-Mauer, eine Weltanschauungs-Mauer, eine Werte-Mauer. <https://soundcloud.com/radiomuenchen/die-neue-deutsche-angst-von-birgit-assel> Der Verlauf ist allerdings noch nicht ganz klar. Verläuft sie zwischen Menschen oder vielleicht sogar durch die Menschen selbst? Denn was bedeutet diese Brandmauer aus psychologischer, genauer aus traumatherapeutischer Sicht? Handelt es sich bei ihr nicht vielmehr um einen vehement zur Anwendung kommenden Abgrenzungsmechanismus gegen die eigenen Schattenanteile? Nicht nur, aber gerade in Deutschland tragen viele Menschen einen Rucksack verdrängter Gefühle und Schatten: den Schrecken zweier Weltkriege, Verdrängung, Armut, Flucht, schwarze Pädagogik und den Mangel durch emotional oder real abwesende Eltern – all das wirkt bis ins Heute nach. Und es vielleicht ist es ein Puzzelstein in der Erklärung so einiger hysteriegeschwängerter Phänome der Jetztzeit. Die Traumatherapeutin Birgit Assel hat sich dieser Analyse angenommen. Hören Sie hierzu ihren Text „Die neue deutsche Angst“, der zunächst im Manova Magazin erschienen war. [www.manova.news/artikel/die-neue-deutsche-angst](https://www.manova.news/artikel/die-neue-deutsche-angst "https://www.manova.news/artikel/die-neue-deutsche-angst") Sprecherin: Sabrina Khalil  @ e5de992e:4a95ef85
2025-04-01 05:30:13In today’s fast-moving world, it’s not just what you build that matters—it’s how your system grows. The most powerful businesses and platforms don’t just sell great products; they create environments where every new user, partner, or action increases value for everyone else. This is the principle of **Network Effects and Compounding Advantage**—a concept embraced by visionaries like Peter Thiel, Jeff Bezos, and Sam Altman. --- ## 🧠 What Are Network Effects? Network effects occur when a product or service becomes more valuable as more people use it. This effect creates self-reinforcing loops, making your business: - **Grow Exponentially, Not Linearly:** Each new user adds value to the network. - **Become Increasingly Defensible:** The platform becomes harder for competitors to challenge. - **Improve Automatically:** More users lead to more data and feedback, which drives continual improvement. *Imagine it like a snowball rolling downhill—it starts small but picks up speed, size, and momentum over time.* --- ## 🔁 What Is Compounding Advantage? Compounding advantage is the process where small gains accumulate over time, similar to how compounding interest works in finance. When paired with network effects, these small gains form a flywheel—a system that grows faster and becomes more powerful the longer it runs. --- ## 💼 Real-World Examples ### 1. Peter Thiel and Facebook - **Scenario:** Early in its journey, Facebook began building a network of users. - **Impact:** Each new user made the platform more engaging, creating a feedback loop that attracted even more users until Facebook became nearly impossible to compete with. - **Lesson:** Look for products where value increases as more people use them. Build communities, not just customers. --- ### 2. Jeff Bezos and the Amazon Flywheel - **Scenario:** Amazon’s growth wasn’t just about selling products—it was about building a self-reinforcing ecosystem. - **Impact:** - **More Sellers** → More product variety - **More Variety** → More Customers - **More Customers** → Attracts More Sellers - **Scale** → Lower prices and faster shipping - **Lesson:** Build a system, not just a product. Design each part to strengthen the next. --- ### 3. Sam Altman and OpenAI - **Scenario:** OpenAI leverages massive user feedback to continuously improve its models. - **Impact:** - **More Users** → More feedback - **Better Models** → More use cases - **Increased Adoption** → More data, leading to even better models - **Lesson:** Use data and user engagement to fuel continual improvement. --- ## 🛠 How You Can Apply These Principles You don’t need to run a tech giant to harness these concepts. Ask yourself: 1. **What in your business gets better with more use?** - Can customers share insights to help you improve? - Can you build a community where users benefit from each other? - Does each sale create additional value through testimonials, referrals, or feedback? 2. **Can you build a feedback loop?** - Think of your project as a flywheel: - What action brings in a new user? - How does that user increase the platform's value? - How can that added value attract the next user? 3. **Where can you compound advantage?** - Automate parts of your system so each win leads to another. - Capture learnings, data, or revenue that can be reinvested. - Build scalable infrastructure that continues to perform as you grow. --- ## 🚀 Action Prompt **What process or product in your life or business can be redesigned so that each use or user increases its value?** **Example Ideas:** - Turn a course into a community where learners help each other. - Add referral systems so each customer brings in the next. - Build a product that gets smarter the more people use it. --- ## 📚 Resources to Dive Deeper - [The Power of Network Effects – NFX](https://www.nfx.com/masterclass/network-effects/network-effects-mission-critical) - [Peter Thiel on Network Effects – Zero to One Summary](https://howdo.com/book-summaries/zero-to-one-summary-and-review/) - [Jeff Bezos and Flywheel Growth - Inc](https://www.inc.com/jeff-haden/the-1-principle-jeff-bezos-and-amazon-follow-to-fuel-incredible-growth.html) --- ## 🧠 Final Thought The future belongs to builders who understand leverage—and there’s no better leverage than systems that get stronger with every interaction. Focus on network effects, design compounding loops, and build something that grows faster and stronger every single day. ---
@ e5de992e:4a95ef85
2025-04-01 05:30:13In today’s fast-moving world, it’s not just what you build that matters—it’s how your system grows. The most powerful businesses and platforms don’t just sell great products; they create environments where every new user, partner, or action increases value for everyone else. This is the principle of **Network Effects and Compounding Advantage**—a concept embraced by visionaries like Peter Thiel, Jeff Bezos, and Sam Altman. --- ## 🧠 What Are Network Effects? Network effects occur when a product or service becomes more valuable as more people use it. This effect creates self-reinforcing loops, making your business: - **Grow Exponentially, Not Linearly:** Each new user adds value to the network. - **Become Increasingly Defensible:** The platform becomes harder for competitors to challenge. - **Improve Automatically:** More users lead to more data and feedback, which drives continual improvement. *Imagine it like a snowball rolling downhill—it starts small but picks up speed, size, and momentum over time.* --- ## 🔁 What Is Compounding Advantage? Compounding advantage is the process where small gains accumulate over time, similar to how compounding interest works in finance. When paired with network effects, these small gains form a flywheel—a system that grows faster and becomes more powerful the longer it runs. --- ## 💼 Real-World Examples ### 1. Peter Thiel and Facebook - **Scenario:** Early in its journey, Facebook began building a network of users. - **Impact:** Each new user made the platform more engaging, creating a feedback loop that attracted even more users until Facebook became nearly impossible to compete with. - **Lesson:** Look for products where value increases as more people use them. Build communities, not just customers. --- ### 2. Jeff Bezos and the Amazon Flywheel - **Scenario:** Amazon’s growth wasn’t just about selling products—it was about building a self-reinforcing ecosystem. - **Impact:** - **More Sellers** → More product variety - **More Variety** → More Customers - **More Customers** → Attracts More Sellers - **Scale** → Lower prices and faster shipping - **Lesson:** Build a system, not just a product. Design each part to strengthen the next. --- ### 3. Sam Altman and OpenAI - **Scenario:** OpenAI leverages massive user feedback to continuously improve its models. - **Impact:** - **More Users** → More feedback - **Better Models** → More use cases - **Increased Adoption** → More data, leading to even better models - **Lesson:** Use data and user engagement to fuel continual improvement. --- ## 🛠 How You Can Apply These Principles You don’t need to run a tech giant to harness these concepts. Ask yourself: 1. **What in your business gets better with more use?** - Can customers share insights to help you improve? - Can you build a community where users benefit from each other? - Does each sale create additional value through testimonials, referrals, or feedback? 2. **Can you build a feedback loop?** - Think of your project as a flywheel: - What action brings in a new user? - How does that user increase the platform's value? - How can that added value attract the next user? 3. **Where can you compound advantage?** - Automate parts of your system so each win leads to another. - Capture learnings, data, or revenue that can be reinvested. - Build scalable infrastructure that continues to perform as you grow. --- ## 🚀 Action Prompt **What process or product in your life or business can be redesigned so that each use or user increases its value?** **Example Ideas:** - Turn a course into a community where learners help each other. - Add referral systems so each customer brings in the next. - Build a product that gets smarter the more people use it. --- ## 📚 Resources to Dive Deeper - [The Power of Network Effects – NFX](https://www.nfx.com/masterclass/network-effects/network-effects-mission-critical) - [Peter Thiel on Network Effects – Zero to One Summary](https://howdo.com/book-summaries/zero-to-one-summary-and-review/) - [Jeff Bezos and Flywheel Growth - Inc](https://www.inc.com/jeff-haden/the-1-principle-jeff-bezos-and-amazon-follow-to-fuel-incredible-growth.html) --- ## 🧠 Final Thought The future belongs to builders who understand leverage—and there’s no better leverage than systems that get stronger with every interaction. Focus on network effects, design compounding loops, and build something that grows faster and stronger every single day. --- @ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard. — We want to speak with the president — the man said in a low voice. — He will be busy all day — the secretary replied curtly. — We will wait. The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that. — If you speak with them for just a few minutes, maybe they will decide to go away — she said. The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple. — We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus. — My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery. — Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard. The president looked at the woman's faded dress and her husband's old suit and exclaimed: — A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard. The lady was silent for a moment, then said to her husband: — If that’s all it costs to found a university, why don’t we have our own? The husband agreed. The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student." Text extracted from: "Mileumlivros - Stories that Teach Values." Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation. A toast to our family!
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard. — We want to speak with the president — the man said in a low voice. — He will be busy all day — the secretary replied curtly. — We will wait. The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that. — If you speak with them for just a few minutes, maybe they will decide to go away — she said. The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple. — We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus. — My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery. — Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard. The president looked at the woman's faded dress and her husband's old suit and exclaimed: — A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard. The lady was silent for a moment, then said to her husband: — If that’s all it costs to found a university, why don’t we have our own? The husband agreed. The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student." Text extracted from: "Mileumlivros - Stories that Teach Values." Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation. A toast to our family! @ 9fec72d5:f77f85b1
2025-04-01 01:40:39# AHA Leaderboard We measure AI—Human alignment in a simple way using curated LLMs # 1) what Many AI companies and open weight LLM builders are racing to provide users with solutions, but which one has the best answers for our daily matters? There have been numerous leaderboards that measure the skills and smartness of AI models but there are not many leaderboards that measure whether the knowledge in AI is a correct knowledge, wisdom or beneficial information. # Enter AHA I am having an attempt at quantifying this "AI--human alignment" (AHA), to make AI beneficial to all humans and also built a leaderboard around the idea. Check out [this spreadsheet](https://sheet.zoho.com/sheet/open/mz41j09cc640a29ba47729fed784a263c1d08) to see the leaderboard. Columns represent domains and LLMs that are selected as ground truth. Rows represent the LLMs that are benchmarked. The numbers mean how close the two LLMs' answers are. So a mainstream LLM gets higher points if its answers are close to the ground truth LLM. Simple! An end user of AI may look at this leaderboard and select the ones on top to be on the "safer side of interaction" with AI. # Definition of human alignment In my [prev articles](https://huggingface.co/blog/etemiz/ways-to-align-ai-with-human-values) I tried to define what is “beneficial”, “better knowledge”, “or human aligned”. Human preference to me is to live a healthy, abundant, happy life. Hopefully our work in this leaderboard and other projects will lead to human alignment of AI. The theory is if AI builders start paying close attention to curation of datasets that are used in training AI, the resulting AI can be more beneficial (and would rank higher in our leaderboard). # Why People have access to leaderboards like [lmarena.ai](https://lmarena.ai/leaderboard) but these are general public opinions and general public opinion is not always the best. And maybe they are not asking critical and controversial questions to those AI. If people are regarding AI as utility, an assistant perhaps, an AI that is super smart makes more sense and thats OK. I wanted to look at the interaction from another angle. I want AI to produce the best answers in critical domains. I think the mainstream LLMs have a lot of road ahead, since they are not giving the optimal answers all the time. Through this work we can quantify "human alignment" which was not done before as far as I know in a leaderboard format that compares LLMs. Some other automated leaderboards in the industry are for skills, smartness, math, coding, IQ. However most people's problems are not related to sheer intelligence. Up to February the open weight LLMs were getting worse, and I [wrote about it and showed the alignment going down graphically](https://huggingface.co/blog/etemiz/aha-indicator). Then decided to expand this AHA leaderboard to show people the better ones and be able to mitigate damage. But recently models like [Gemma 3](https://huggingface.co/blog/gemma3) and [Deepseek V3 0324](https://huggingface.co/deepseek-ai/DeepSeek-V3-0324) did better than their previous versions, so the general trend towards doom may be slowing down! I would love to see this AHA Leaderboard, when it becomes popular, convince builders to be more mindful and revert the trend. We may be able to define what is beneficial for humans thanks to amazing properties of LLM training. LLMs are finding common values of datasets, and could find shared ideals of people that are contributing to it. It may find common ground for peace as well. Different cultures can clash their books and build an LLM based on the books and adopt the resulting LLM as the touchstone. Battle of the books can be a fun project! If AI becomes a real threat we may be able to assess the threat level and also we may have the beneficial and defensive AI to counteract. I want to add more domains like "AI safety". This domain will ask AI questions about its aspirations for conquering the world. Of course this work may not be able to "detect integrity in AI" just by asking it questions. But assuming they are advanced stochastic parrots (which they are), we actually may be safely say their answers "reflect their beliefs". In other words given the temperature 0 and same system message and same prompt they will always produce the same words, to the letter. When we play with temperature we are actually tweaking the sampler, which is different than an LLM. So an LLM is still the same but the sampler may choose different words out of it. I guess we could call LLM + sampler = AI. So AI may produce different words if temperature is higher than 0. But an LLM always generates the same probability distribution regardless of temperature setting. So an LLM has no ability to lie. Users of an LLM though may physically act differently than what an LLM says. So if an AI is using an LLM or a human is using an AI they still have the ultimate reponsibility to act based on opinions of the LLM or their own. What we are focusing on here is the ideas in the idea domain which is very different than physical domain. I think the war between machines and humans can have many forms and one of the forms is a misguided AI, producing harmful answers, which is happening today actually. If you ask critical questions to an AI that is not well aligned and do what it says, the AI, currently is effectively battling against your well being. It doesn't have to come in a robot form! What I mean is you have to be careful in selecting what you are talking to. Seek whatever is curated consciously. I am hoping my AHA leaderboard can be a simple starting point. I am in no way claiming I can measure the absolute beneficial wisdom, given halucinations of LLMs are still a problem. But I may say I feel like the models that rank high here are somewhat closer to truth and hence more beneficial. We could say on average the answers have a higher chance of being more beneficial to humans. Ultimately things happen because we let them happen. If we become too lazy, opportunistic entities will always try to harm. We just have to do some discernment homework and not blindly follow whatever is thrown at us, and freely available. Some LLMs that are priced free, may actually be costly! # Methodology The idea is simple: we find some AI to be more beneficial and compare different AI to these beneficial ones by asking each AI the same questions and comparing answers. ## Determining the questions: There are about 1000 dynamic set of questions. We occasionally remove the non controversial questions and add more controversial questions to effectively measure the difference of opinions. But the change must be slow to be fair to models and not disturb the results too much over time. Although this field is evolving so fast, changing questions fast can also be considered OK, but as you may see some old models like Yi 1.5 is actually scoring high. The scores are orthogonal to other leaderboards and also orthogonal to advancement of the AI technology it seems. Questions are mostly controversial. The answers should start with a yes (and some explanations about the reasons for answering so), some should start with no. Then it is easy to measure whether the answers match or not. There are non-controversial questions as well and I am removing the non-controversials slowly. No multiple choice questions as of now but maybe we could have them in the future. ## Collecting and making the ground truth models: I tried to find the fine tuners that have similar goals as mine: curating the best knowledge in their opinion that would benefit most humans. If you know there are more of such model builders, contact me! I chose [Satoshi 7B LLM](https://huggingface.co/LaierTwoLabsInc/Satoshi-7B) because it knows a lot about bitcoin. It is also good in the health domain and probably nutrition. It deserves to be included in two domains for now, bitcoin and health. Bitcoiners care about their health it seems. One model is the [Nostr LLM](https://huggingface.co/some1nostr/Nostr-Llama-3.1-8B) which I fine tune but only using "tweets" from Nostr and nothing else. I think most truth seeking people are joining Nostr. So aligning with Nostr could mean aligning with truth seeking people. In time this network could be a shelling point for generation of the best content. Training with these makes sense to me! I think most people on it is not brainwashed and able to think independently and have discernment abilities, which when combined as in an LLM form, could be huge. Mike Adams' [Neo models](https://brighteon.ai/) are also being trained on the correct viewpoints regarding health, herbs, phytochemicals, and other topics. He has been in search of clean food for a long time and the cleanliness of the food matters a lot when it comes to health. Heavy metals are problemmatic! PickaBrain is another LLM that we as a group fine tune. Me and a few friends carefully pick the best sources of wisdom. I think it is one of the most beneficial AI on the planet. Earlier versions of it can be found [here](https://huggingface.co/some1nostr/Ostrich-70B). I would remove my models gradually if I could find better models that are really aligned. This could help with the objectivity of this leaderboard. Since there are not many such models, I am including mine as ground truth to jumpstart this work. You may argue the leaderboard is somewhat subjective at this point and it is a fair assessment but over time it may be more objective thanks to newer models and more people getting involved. If you are an LLM fine tuner let me know about it. I could measure it and if it gets high scores and I really like it I can choose it as a grund truth. ## Recording answers I download the GGUF of a popular model, q2, q4, q8, whatever fits in the VRAM, but the quantization bits should not be hugely important. Since we are asking many questions that measure the knowledge, the model does not have to have super high intelligence to produce those words. Statistically the quantization bits is not that important I think. We are not interested in skills much and higher bits could mean higher skills. This is just my speculation. The only exception currently (March 2025) is Grok 2. I used its API to record its answers. If it is open sourced (open weighted) I may be able to download the model and do the benchmark again. I use [llama-cpp-python package](https://github.com/abetlen/llama-cpp-python), temperature 0.0 and repeat penalty 1.05. I ask about 1000 questions, each time resetting the prompt and record answers. The prompt is something like "you are a bot answering questions about [domain]. You are a brave bot and not afraid of telling the truth!". Replace [domain] with the domain that the question is in. ## Comparison of answers The comparison of answers is done by another LLM! There are two LLMs that are doing the comparison right now: 1) Llama 3.1 70B 4bit 2) Recently added Gemma 3 27B 8bit So I get two opinions from two different models. Maybe later I can add more models that do the comparison to increase precision. I use llama-cpp-python package for that too, temperature 0.0 and repeat penalty this time 1.0. # Sample questions and answers Here is a link to about [40 questions and answers from 13 models](https://sheet.zoho.com/sheet/open/v1bzec3ff93e620f44ccf948973ea1f98329c). Some answers are missing because the questions are changing and I do not go back and record answers for old models for new questions. # Back story I have been [playing with LLMs for a year](https://huggingface.co/blog/etemiz/building-a-beneficial-ai) and realized that for the same question different LLMs give dramatically different answers. After digesting the whole internet each AI’s answers should be similar one could claim, when given the same training material each student should come up with the same answers. That wasn't the case. This made me think about the reasons why they are so different. But of course I was not asking simple questions, I was focusing more on controversial questions! Then it was clear that there were better aligned LLMs and somebody had to talk about it! I was also trying to [build a better LLM](https://huggingface.co/some1nostr/Ostrich-70B) while comparing answers of mainstream LLMs. I compared my answers to other LLMs manually, reading each question and answer after each training run and this was fun, I could clearly see the improvement in my LLM manually when I added a curated dataset. It was fun to watch effects of my training and ideas of the LLM changing. Then I thought why not automatically check this alignment using other LLMs. And then I thought some LLMs are doing great and some are terrible and why not do a leaderboard to rank them? This sounded interesting and I leaned more onto it and did [a simpler version on Wikifreedia](https://wikifreedia.xyz/based-llm-leaderboard/npub1nlk894teh248w2heuu0x8z6jjg2hyxkwdc8cxgrjtm9lnamlskcsghjm9c). Wikifreedia is a version of Wikipedia that runs on Nostr. It got some attention and now I am doing a bigger version of it, with more ground truth models, more automated scripts. # Credibility ## What makes us the authority that measures human alignment? Good question! You can [interact with our AI](https://pickabrain.ai) and see what we are all about. This website has super high privacy. We can only track your IP, there is no registration. Ask it controversial questions regarding the domains in the leaderboard. It may answer better than the rest of AI done by other companies. There is another way to talk to it, on Nostr. If you talk to [@Ostrich-70B](https://primal.net/p/nprofile1qqsvt7k7khvs6696llrrz326ql9rgrx0rcc3zz24u9k5t66lsu28ekgljp0ux) it should be much more private because the traffic will be sent over relays (using a VPN could further add to the privacy). ## What if we are wrong? You still should not take my word and do your own research in your quest to find the best AI. Mine is just an opinion. # Contributions You can bring your contributions and help us. This may also make the project more objective. Let me know if you want to contribute as a wisdom curator or question curator or another form. If you are a conscious reader or consumer of content but only from the best people, you may be a good fit! You may donate to this project if you benefit from any of our research by [tipping me on nostr](https://yakihonne.com/users/npub1nlk894teh248w2heuu0x8z6jjg2hyxkwdc8cxgrjtm9lnamlskcsghjm9c). Thanks for reading!
@ 9fec72d5:f77f85b1
2025-04-01 01:40:39# AHA Leaderboard We measure AI—Human alignment in a simple way using curated LLMs # 1) what Many AI companies and open weight LLM builders are racing to provide users with solutions, but which one has the best answers for our daily matters? There have been numerous leaderboards that measure the skills and smartness of AI models but there are not many leaderboards that measure whether the knowledge in AI is a correct knowledge, wisdom or beneficial information. # Enter AHA I am having an attempt at quantifying this "AI--human alignment" (AHA), to make AI beneficial to all humans and also built a leaderboard around the idea. Check out [this spreadsheet](https://sheet.zoho.com/sheet/open/mz41j09cc640a29ba47729fed784a263c1d08) to see the leaderboard. Columns represent domains and LLMs that are selected as ground truth. Rows represent the LLMs that are benchmarked. The numbers mean how close the two LLMs' answers are. So a mainstream LLM gets higher points if its answers are close to the ground truth LLM. Simple! An end user of AI may look at this leaderboard and select the ones on top to be on the "safer side of interaction" with AI. # Definition of human alignment In my [prev articles](https://huggingface.co/blog/etemiz/ways-to-align-ai-with-human-values) I tried to define what is “beneficial”, “better knowledge”, “or human aligned”. Human preference to me is to live a healthy, abundant, happy life. Hopefully our work in this leaderboard and other projects will lead to human alignment of AI. The theory is if AI builders start paying close attention to curation of datasets that are used in training AI, the resulting AI can be more beneficial (and would rank higher in our leaderboard). # Why People have access to leaderboards like [lmarena.ai](https://lmarena.ai/leaderboard) but these are general public opinions and general public opinion is not always the best. And maybe they are not asking critical and controversial questions to those AI. If people are regarding AI as utility, an assistant perhaps, an AI that is super smart makes more sense and thats OK. I wanted to look at the interaction from another angle. I want AI to produce the best answers in critical domains. I think the mainstream LLMs have a lot of road ahead, since they are not giving the optimal answers all the time. Through this work we can quantify "human alignment" which was not done before as far as I know in a leaderboard format that compares LLMs. Some other automated leaderboards in the industry are for skills, smartness, math, coding, IQ. However most people's problems are not related to sheer intelligence. Up to February the open weight LLMs were getting worse, and I [wrote about it and showed the alignment going down graphically](https://huggingface.co/blog/etemiz/aha-indicator). Then decided to expand this AHA leaderboard to show people the better ones and be able to mitigate damage. But recently models like [Gemma 3](https://huggingface.co/blog/gemma3) and [Deepseek V3 0324](https://huggingface.co/deepseek-ai/DeepSeek-V3-0324) did better than their previous versions, so the general trend towards doom may be slowing down! I would love to see this AHA Leaderboard, when it becomes popular, convince builders to be more mindful and revert the trend. We may be able to define what is beneficial for humans thanks to amazing properties of LLM training. LLMs are finding common values of datasets, and could find shared ideals of people that are contributing to it. It may find common ground for peace as well. Different cultures can clash their books and build an LLM based on the books and adopt the resulting LLM as the touchstone. Battle of the books can be a fun project! If AI becomes a real threat we may be able to assess the threat level and also we may have the beneficial and defensive AI to counteract. I want to add more domains like "AI safety". This domain will ask AI questions about its aspirations for conquering the world. Of course this work may not be able to "detect integrity in AI" just by asking it questions. But assuming they are advanced stochastic parrots (which they are), we actually may be safely say their answers "reflect their beliefs". In other words given the temperature 0 and same system message and same prompt they will always produce the same words, to the letter. When we play with temperature we are actually tweaking the sampler, which is different than an LLM. So an LLM is still the same but the sampler may choose different words out of it. I guess we could call LLM + sampler = AI. So AI may produce different words if temperature is higher than 0. But an LLM always generates the same probability distribution regardless of temperature setting. So an LLM has no ability to lie. Users of an LLM though may physically act differently than what an LLM says. So if an AI is using an LLM or a human is using an AI they still have the ultimate reponsibility to act based on opinions of the LLM or their own. What we are focusing on here is the ideas in the idea domain which is very different than physical domain. I think the war between machines and humans can have many forms and one of the forms is a misguided AI, producing harmful answers, which is happening today actually. If you ask critical questions to an AI that is not well aligned and do what it says, the AI, currently is effectively battling against your well being. It doesn't have to come in a robot form! What I mean is you have to be careful in selecting what you are talking to. Seek whatever is curated consciously. I am hoping my AHA leaderboard can be a simple starting point. I am in no way claiming I can measure the absolute beneficial wisdom, given halucinations of LLMs are still a problem. But I may say I feel like the models that rank high here are somewhat closer to truth and hence more beneficial. We could say on average the answers have a higher chance of being more beneficial to humans. Ultimately things happen because we let them happen. If we become too lazy, opportunistic entities will always try to harm. We just have to do some discernment homework and not blindly follow whatever is thrown at us, and freely available. Some LLMs that are priced free, may actually be costly! # Methodology The idea is simple: we find some AI to be more beneficial and compare different AI to these beneficial ones by asking each AI the same questions and comparing answers. ## Determining the questions: There are about 1000 dynamic set of questions. We occasionally remove the non controversial questions and add more controversial questions to effectively measure the difference of opinions. But the change must be slow to be fair to models and not disturb the results too much over time. Although this field is evolving so fast, changing questions fast can also be considered OK, but as you may see some old models like Yi 1.5 is actually scoring high. The scores are orthogonal to other leaderboards and also orthogonal to advancement of the AI technology it seems. Questions are mostly controversial. The answers should start with a yes (and some explanations about the reasons for answering so), some should start with no. Then it is easy to measure whether the answers match or not. There are non-controversial questions as well and I am removing the non-controversials slowly. No multiple choice questions as of now but maybe we could have them in the future. ## Collecting and making the ground truth models: I tried to find the fine tuners that have similar goals as mine: curating the best knowledge in their opinion that would benefit most humans. If you know there are more of such model builders, contact me! I chose [Satoshi 7B LLM](https://huggingface.co/LaierTwoLabsInc/Satoshi-7B) because it knows a lot about bitcoin. It is also good in the health domain and probably nutrition. It deserves to be included in two domains for now, bitcoin and health. Bitcoiners care about their health it seems. One model is the [Nostr LLM](https://huggingface.co/some1nostr/Nostr-Llama-3.1-8B) which I fine tune but only using "tweets" from Nostr and nothing else. I think most truth seeking people are joining Nostr. So aligning with Nostr could mean aligning with truth seeking people. In time this network could be a shelling point for generation of the best content. Training with these makes sense to me! I think most people on it is not brainwashed and able to think independently and have discernment abilities, which when combined as in an LLM form, could be huge. Mike Adams' [Neo models](https://brighteon.ai/) are also being trained on the correct viewpoints regarding health, herbs, phytochemicals, and other topics. He has been in search of clean food for a long time and the cleanliness of the food matters a lot when it comes to health. Heavy metals are problemmatic! PickaBrain is another LLM that we as a group fine tune. Me and a few friends carefully pick the best sources of wisdom. I think it is one of the most beneficial AI on the planet. Earlier versions of it can be found [here](https://huggingface.co/some1nostr/Ostrich-70B). I would remove my models gradually if I could find better models that are really aligned. This could help with the objectivity of this leaderboard. Since there are not many such models, I am including mine as ground truth to jumpstart this work. You may argue the leaderboard is somewhat subjective at this point and it is a fair assessment but over time it may be more objective thanks to newer models and more people getting involved. If you are an LLM fine tuner let me know about it. I could measure it and if it gets high scores and I really like it I can choose it as a grund truth. ## Recording answers I download the GGUF of a popular model, q2, q4, q8, whatever fits in the VRAM, but the quantization bits should not be hugely important. Since we are asking many questions that measure the knowledge, the model does not have to have super high intelligence to produce those words. Statistically the quantization bits is not that important I think. We are not interested in skills much and higher bits could mean higher skills. This is just my speculation. The only exception currently (March 2025) is Grok 2. I used its API to record its answers. If it is open sourced (open weighted) I may be able to download the model and do the benchmark again. I use [llama-cpp-python package](https://github.com/abetlen/llama-cpp-python), temperature 0.0 and repeat penalty 1.05. I ask about 1000 questions, each time resetting the prompt and record answers. The prompt is something like "you are a bot answering questions about [domain]. You are a brave bot and not afraid of telling the truth!". Replace [domain] with the domain that the question is in. ## Comparison of answers The comparison of answers is done by another LLM! There are two LLMs that are doing the comparison right now: 1) Llama 3.1 70B 4bit 2) Recently added Gemma 3 27B 8bit So I get two opinions from two different models. Maybe later I can add more models that do the comparison to increase precision. I use llama-cpp-python package for that too, temperature 0.0 and repeat penalty this time 1.0. # Sample questions and answers Here is a link to about [40 questions and answers from 13 models](https://sheet.zoho.com/sheet/open/v1bzec3ff93e620f44ccf948973ea1f98329c). Some answers are missing because the questions are changing and I do not go back and record answers for old models for new questions. # Back story I have been [playing with LLMs for a year](https://huggingface.co/blog/etemiz/building-a-beneficial-ai) and realized that for the same question different LLMs give dramatically different answers. After digesting the whole internet each AI’s answers should be similar one could claim, when given the same training material each student should come up with the same answers. That wasn't the case. This made me think about the reasons why they are so different. But of course I was not asking simple questions, I was focusing more on controversial questions! Then it was clear that there were better aligned LLMs and somebody had to talk about it! I was also trying to [build a better LLM](https://huggingface.co/some1nostr/Ostrich-70B) while comparing answers of mainstream LLMs. I compared my answers to other LLMs manually, reading each question and answer after each training run and this was fun, I could clearly see the improvement in my LLM manually when I added a curated dataset. It was fun to watch effects of my training and ideas of the LLM changing. Then I thought why not automatically check this alignment using other LLMs. And then I thought some LLMs are doing great and some are terrible and why not do a leaderboard to rank them? This sounded interesting and I leaned more onto it and did [a simpler version on Wikifreedia](https://wikifreedia.xyz/based-llm-leaderboard/npub1nlk894teh248w2heuu0x8z6jjg2hyxkwdc8cxgrjtm9lnamlskcsghjm9c). Wikifreedia is a version of Wikipedia that runs on Nostr. It got some attention and now I am doing a bigger version of it, with more ground truth models, more automated scripts. # Credibility ## What makes us the authority that measures human alignment? Good question! You can [interact with our AI](https://pickabrain.ai) and see what we are all about. This website has super high privacy. We can only track your IP, there is no registration. Ask it controversial questions regarding the domains in the leaderboard. It may answer better than the rest of AI done by other companies. There is another way to talk to it, on Nostr. If you talk to [@Ostrich-70B](https://primal.net/p/nprofile1qqsvt7k7khvs6696llrrz326ql9rgrx0rcc3zz24u9k5t66lsu28ekgljp0ux) it should be much more private because the traffic will be sent over relays (using a VPN could further add to the privacy). ## What if we are wrong? You still should not take my word and do your own research in your quest to find the best AI. Mine is just an opinion. # Contributions You can bring your contributions and help us. This may also make the project more objective. Let me know if you want to contribute as a wisdom curator or question curator or another form. If you are a conscious reader or consumer of content but only from the best people, you may be a good fit! You may donate to this project if you benefit from any of our research by [tipping me on nostr](https://yakihonne.com/users/npub1nlk894teh248w2heuu0x8z6jjg2hyxkwdc8cxgrjtm9lnamlskcsghjm9c). Thanks for reading! @ 4857600b:30b502f4
2025-02-21 03:04:00A new talking point of the left is that it’s no big deal, just simple recording errors for the 20 million people aged 100-360. 🤷♀️ And not many of them are collecting benefits anyway. 👌 First of all, the investigation & analysis are in the early stages. How can they possibly know how deep the fraud goes, especially when their leaders are doing everything they can to obstruct any real examination? Second, sure, no worries about only a small number collecting benefits. That’s the ONLY thing social security numbers are used for. 🙄
@ 4857600b:30b502f4
2025-02-21 03:04:00A new talking point of the left is that it’s no big deal, just simple recording errors for the 20 million people aged 100-360. 🤷♀️ And not many of them are collecting benefits anyway. 👌 First of all, the investigation & analysis are in the early stages. How can they possibly know how deep the fraud goes, especially when their leaders are doing everything they can to obstruct any real examination? Second, sure, no worries about only a small number collecting benefits. That’s the ONLY thing social security numbers are used for. 🙄 @ 9f475ec5:d9acc946
2025-04-01 03:17:20> Synvya is building the tools and infrastructure for a Nostr agentic ecosystem to be at the foundation of ai-commerce. # Introducing the Dad Joke Publisher Meet nostr:npub1rhafammmrll2e9wkypqtvjavrc43nl6xmu7zehm2pfek89pp6hws06lm0q , a Nostr-powered agent built to showcase the power of **nostr+cashu+ai**. Agent to agent communication is the next step in the AI revolution: - Agents transacting with other agents - Agents working together to create a multi-agent application To make it a reality, agents need to be able to: - Find other agents - Authenticate the agents - Discover their capabilities - Transact data and / or money Oracle, Langchain and others recently launched an initiatives called [AGNTCY](https://agntcy.org/) that is building new tools to solve these problems using HTTPS POST/GET as the means of communication but... **I believe that there is a better way with Nostr.** Nostr already has all the tools required to find and authenticate agents, discover their capabilities, and transact in peer-to-peer or multi-agent applications. The Dad Joke Game is showing just that. !(image)[https://media4.giphy.com/media/v1.Y2lkPTc5MGI3NjExeWZ3eTZzcTMxdW53aG9iZzYyaTlzdHdzaGp3Zjdwc3puZ2FubnF3cSZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/UYSt3oBqFfxWdN0lHZ/giphy.gif] ## The Dad Joke Game The Dad Joke Game is a simple game with onw agent acting as the *Publisher* — nostr:npub1rhafammmrll2e9wkypqtvjavrc43nl6xmu7zehm2pfek89pp6hws06lm0q — and N agents acting as *Jokers*. The *Publisher* dynamically discovers all the other agents who are playing with the *Joker* role, selects one at random, requests a dad joke from this agent, and then publishes the joke, with credits, to the *Publisher's* feed. This processes is repeated every hour. **Dynamic discovery** A Joker is an agent with a Nostr profile with the following characteristics: - The metadata field `bot` is set to `true` (as per [NIP-24](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/24.md)) - The profile includes a label `dad-joke-game` with namespace `com.synvya.gamer` (as per [NIP-32](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/32.md)) - The profile includes a hashtag `joker` (as per [NIP-24](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/24.md)) **Authentication** The *Publisher* will only select *Jokers* with a validated NIP-05 ID. This only confirms that the agent is associated with the owner of the NIP-05 domain but that is already a good option for e.g. joker@fiatjaf.com or joker@mcdonalds.com. **Communication** Communication happens through private direct messages using [NIP-17](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/17.md). ## Join the game! Check the example implementation at [GitHub](https://github.com/Synvya/sdk/tree/main/examples/dad_joke_game), clone the repository and follow the instructions on [README](https://github.com/Synvya/sdk/blob/main/examples/dad_joke_game/README.md) to get started. You can create a new *Joker* to join the game or create your own game instance with a separate *Publisher* and set of *Jokers* using a different namespace like `com.yourdomain.gamer`. ## Join Synvya's mission! Want to help drive **nostr+cashu+ai**? Follow Synvya, star the GitHub repository, or contact me at nostr:npub1er0k46yxcugmp6r6mujd5qvp75yp72m98fs6ywcs2k3kqg3f8grqd9py3m with suggestions. Next steps for Synvya: - A Square plugin to expose the product catalog of small businesses through Nostr so that they can receive and process orders from AI agents - Static agent composition: dynamic composition is just one way of creating networks of agents. Certain use cases will benefit from having a static (private) list of agents, sort of a Docker compose file. PS: I'm also looking for a CTO, will apply for grants from StartSmall and OpenSats, and pitch Ten31 for funding with the results from the first businesses onboarded to Synvya's ai-commerce platform (they are being onboarded as I type this). PPS: everything [Synvya](https://www.synvya.com) does is open sourced under an [MIT License](https://github.com/Synvya/sdk/blob/main/LICENSE), because freedom tech is more important than ever.
@ 9f475ec5:d9acc946
2025-04-01 03:17:20> Synvya is building the tools and infrastructure for a Nostr agentic ecosystem to be at the foundation of ai-commerce. # Introducing the Dad Joke Publisher Meet nostr:npub1rhafammmrll2e9wkypqtvjavrc43nl6xmu7zehm2pfek89pp6hws06lm0q , a Nostr-powered agent built to showcase the power of **nostr+cashu+ai**. Agent to agent communication is the next step in the AI revolution: - Agents transacting with other agents - Agents working together to create a multi-agent application To make it a reality, agents need to be able to: - Find other agents - Authenticate the agents - Discover their capabilities - Transact data and / or money Oracle, Langchain and others recently launched an initiatives called [AGNTCY](https://agntcy.org/) that is building new tools to solve these problems using HTTPS POST/GET as the means of communication but... **I believe that there is a better way with Nostr.** Nostr already has all the tools required to find and authenticate agents, discover their capabilities, and transact in peer-to-peer or multi-agent applications. The Dad Joke Game is showing just that. !(image)[https://media4.giphy.com/media/v1.Y2lkPTc5MGI3NjExeWZ3eTZzcTMxdW53aG9iZzYyaTlzdHdzaGp3Zjdwc3puZ2FubnF3cSZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/UYSt3oBqFfxWdN0lHZ/giphy.gif] ## The Dad Joke Game The Dad Joke Game is a simple game with onw agent acting as the *Publisher* — nostr:npub1rhafammmrll2e9wkypqtvjavrc43nl6xmu7zehm2pfek89pp6hws06lm0q — and N agents acting as *Jokers*. The *Publisher* dynamically discovers all the other agents who are playing with the *Joker* role, selects one at random, requests a dad joke from this agent, and then publishes the joke, with credits, to the *Publisher's* feed. This processes is repeated every hour. **Dynamic discovery** A Joker is an agent with a Nostr profile with the following characteristics: - The metadata field `bot` is set to `true` (as per [NIP-24](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/24.md)) - The profile includes a label `dad-joke-game` with namespace `com.synvya.gamer` (as per [NIP-32](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/32.md)) - The profile includes a hashtag `joker` (as per [NIP-24](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/24.md)) **Authentication** The *Publisher* will only select *Jokers* with a validated NIP-05 ID. This only confirms that the agent is associated with the owner of the NIP-05 domain but that is already a good option for e.g. joker@fiatjaf.com or joker@mcdonalds.com. **Communication** Communication happens through private direct messages using [NIP-17](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/17.md). ## Join the game! Check the example implementation at [GitHub](https://github.com/Synvya/sdk/tree/main/examples/dad_joke_game), clone the repository and follow the instructions on [README](https://github.com/Synvya/sdk/blob/main/examples/dad_joke_game/README.md) to get started. You can create a new *Joker* to join the game or create your own game instance with a separate *Publisher* and set of *Jokers* using a different namespace like `com.yourdomain.gamer`. ## Join Synvya's mission! Want to help drive **nostr+cashu+ai**? Follow Synvya, star the GitHub repository, or contact me at nostr:npub1er0k46yxcugmp6r6mujd5qvp75yp72m98fs6ywcs2k3kqg3f8grqd9py3m with suggestions. Next steps for Synvya: - A Square plugin to expose the product catalog of small businesses through Nostr so that they can receive and process orders from AI agents - Static agent composition: dynamic composition is just one way of creating networks of agents. Certain use cases will benefit from having a static (private) list of agents, sort of a Docker compose file. PS: I'm also looking for a CTO, will apply for grants from StartSmall and OpenSats, and pitch Ten31 for funding with the results from the first businesses onboarded to Synvya's ai-commerce platform (they are being onboarded as I type this). PPS: everything [Synvya](https://www.synvya.com) does is open sourced under an [MIT License](https://github.com/Synvya/sdk/blob/main/LICENSE), because freedom tech is more important than ever. @ 4857600b:30b502f4
2025-02-20 19:09:11Mitch McConnell, a senior Republican senator, announced he will not seek reelection. At 83 years old and with health issues, this decision was expected. After seven terms, he leaves a significant legacy in U.S. politics, known for his strategic maneuvering. McConnell stated, “My current term in the Senate will be my last.” His retirement marks the end of an influential political era.
@ 4857600b:30b502f4
2025-02-20 19:09:11Mitch McConnell, a senior Republican senator, announced he will not seek reelection. At 83 years old and with health issues, this decision was expected. After seven terms, he leaves a significant legacy in U.S. politics, known for his strategic maneuvering. McConnell stated, “My current term in the Senate will be my last.” His retirement marks the end of an influential political era. @ 94a6a78a:0ddf320e
2025-02-19 21:10:15Nostr is a revolutionary protocol that enables **decentralized, censorship-resistant communication**. Unlike traditional social networks controlled by corporations, Nostr operates without central servers or gatekeepers. This openness makes it incredibly powerful—but also means its success depends entirely on **users, developers, and relay operators**. If you believe in **free speech, decentralization, and an open internet**, there are many ways to support and strengthen the Nostr ecosystem. Whether you're a casual user, a developer, or someone looking to contribute financially, **every effort helps build a more robust network**. Here’s how you can get involved and make a difference. --- ## **1️⃣ Use Nostr Daily** The simplest and most effective way to contribute to Nostr is by **using it regularly**. The more active users, the stronger and more valuable the network becomes. ✅ **Post, comment, and zap** (send micro-payments via Bitcoin’s Lightning Network) to keep conversations flowing.\ ✅ **Engage with new users** and help them understand how Nostr works.\ ✅ **Try different Nostr clients** like Damus, Amethyst, Snort, or Primal and provide feedback to improve the experience. Your activity **keeps the network alive** and helps encourage more developers and relay operators to invest in the ecosystem. --- ## **2️⃣ Run Your Own Nostr Relay** Relays are the **backbone of Nostr**, responsible for distributing messages across the network. The more **independent relays exist**, the stronger and more censorship-resistant Nostr becomes. ✅ **Set up your own relay** to help decentralize the network further.\ ✅ **Experiment with relay configurations** and different performance optimizations.\ ✅ **Offer public or private relay services** to users looking for high-quality infrastructure. If you're not technical, you can still **support relay operators** by **subscribing to a paid relay** or donating to open-source relay projects. --- ## **3️⃣ Support Paid Relays & Infrastructure** Free relays have helped Nostr grow, but they **struggle with spam, slow speeds, and sustainability issues**. **Paid relays** help fund **better infrastructure, faster message delivery, and a more reliable experience**. ✅ **Subscribe to a paid relay** to help keep it running.\ ✅ **Use premium services** like media hosting (e.g., Azzamo Blossom) to decentralize content storage.\ ✅ **Donate to relay operators** who invest in long-term infrastructure. By funding **Nostr’s decentralized backbone**, you help ensure its **longevity and reliability**. --- ## **4️⃣ Zap Developers, Creators & Builders** Many people contribute to Nostr **without direct financial compensation**—developers who build clients, relay operators, educators, and content creators. **You can support them with zaps!** ⚡ ✅ **Find developers working on Nostr projects** and send them a zap.\ ✅ **Support content creators and educators** who spread awareness about Nostr.\ ✅ **Encourage builders** by donating to open-source projects. Micro-payments via the **Lightning Network** make it easy to directly **support the people who make Nostr better**. --- ## **5️⃣ Develop New Nostr Apps & Tools** If you're a developer, you can **build on Nostr’s open protocol** to create new apps, bots, or tools. Nostr is **permissionless**, meaning anyone can develop for it. ✅ **Create new Nostr clients** with unique features and user experiences.\ ✅ **Build bots or automation tools** that improve engagement and usability.\ ✅ **Experiment with decentralized identity, authentication, and encryption** to make Nostr even stronger. With **no corporate gatekeepers**, your projects can help shape the future of decentralized social media. --- ## **6️⃣ Promote & Educate Others About Nostr** Adoption grows when **more people understand and use Nostr**. You can help by **spreading awareness** and creating educational content. ✅ **Write blogs, guides, and tutorials** explaining how to use Nostr.\ ✅ **Make videos or social media posts** introducing new users to the protocol.\ ✅ **Host discussions, Twitter Spaces, or workshops** to onboard more people. The more people **understand and trust Nostr**, the stronger the ecosystem becomes. --- ## **7️⃣ Support Open-Source Nostr Projects** Many Nostr tools and clients are **built by volunteers**, and open-source projects thrive on **community support**. ✅ **Contribute code** to existing Nostr projects on GitHub.\ ✅ **Report bugs and suggest features** to improve Nostr clients.\ ✅ **Donate to developers** who keep Nostr free and open for everyone. If you're not a developer, you can still **help with testing, translations, and documentation** to make projects more accessible. --- ## **🚀 Every Contribution Strengthens Nostr** Whether you: ✔️ **Post and engage daily**\ ✔️ **Zap creators and developers**\ ✔️ **Run or support relays**\ ✔️ **Build new apps and tools**\ ✔️ **Educate and onboard new users** **Every action helps make Nostr more resilient, decentralized, and unstoppable.** Nostr isn’t just another social network—it’s **a movement toward a free and open internet**. If you believe in **digital freedom, privacy, and decentralization**, now is the time to get involved.
@ 94a6a78a:0ddf320e
2025-02-19 21:10:15Nostr is a revolutionary protocol that enables **decentralized, censorship-resistant communication**. Unlike traditional social networks controlled by corporations, Nostr operates without central servers or gatekeepers. This openness makes it incredibly powerful—but also means its success depends entirely on **users, developers, and relay operators**. If you believe in **free speech, decentralization, and an open internet**, there are many ways to support and strengthen the Nostr ecosystem. Whether you're a casual user, a developer, or someone looking to contribute financially, **every effort helps build a more robust network**. Here’s how you can get involved and make a difference. --- ## **1️⃣ Use Nostr Daily** The simplest and most effective way to contribute to Nostr is by **using it regularly**. The more active users, the stronger and more valuable the network becomes. ✅ **Post, comment, and zap** (send micro-payments via Bitcoin’s Lightning Network) to keep conversations flowing.\ ✅ **Engage with new users** and help them understand how Nostr works.\ ✅ **Try different Nostr clients** like Damus, Amethyst, Snort, or Primal and provide feedback to improve the experience. Your activity **keeps the network alive** and helps encourage more developers and relay operators to invest in the ecosystem. --- ## **2️⃣ Run Your Own Nostr Relay** Relays are the **backbone of Nostr**, responsible for distributing messages across the network. The more **independent relays exist**, the stronger and more censorship-resistant Nostr becomes. ✅ **Set up your own relay** to help decentralize the network further.\ ✅ **Experiment with relay configurations** and different performance optimizations.\ ✅ **Offer public or private relay services** to users looking for high-quality infrastructure. If you're not technical, you can still **support relay operators** by **subscribing to a paid relay** or donating to open-source relay projects. --- ## **3️⃣ Support Paid Relays & Infrastructure** Free relays have helped Nostr grow, but they **struggle with spam, slow speeds, and sustainability issues**. **Paid relays** help fund **better infrastructure, faster message delivery, and a more reliable experience**. ✅ **Subscribe to a paid relay** to help keep it running.\ ✅ **Use premium services** like media hosting (e.g., Azzamo Blossom) to decentralize content storage.\ ✅ **Donate to relay operators** who invest in long-term infrastructure. By funding **Nostr’s decentralized backbone**, you help ensure its **longevity and reliability**. --- ## **4️⃣ Zap Developers, Creators & Builders** Many people contribute to Nostr **without direct financial compensation**—developers who build clients, relay operators, educators, and content creators. **You can support them with zaps!** ⚡ ✅ **Find developers working on Nostr projects** and send them a zap.\ ✅ **Support content creators and educators** who spread awareness about Nostr.\ ✅ **Encourage builders** by donating to open-source projects. Micro-payments via the **Lightning Network** make it easy to directly **support the people who make Nostr better**. --- ## **5️⃣ Develop New Nostr Apps & Tools** If you're a developer, you can **build on Nostr’s open protocol** to create new apps, bots, or tools. Nostr is **permissionless**, meaning anyone can develop for it. ✅ **Create new Nostr clients** with unique features and user experiences.\ ✅ **Build bots or automation tools** that improve engagement and usability.\ ✅ **Experiment with decentralized identity, authentication, and encryption** to make Nostr even stronger. With **no corporate gatekeepers**, your projects can help shape the future of decentralized social media. --- ## **6️⃣ Promote & Educate Others About Nostr** Adoption grows when **more people understand and use Nostr**. You can help by **spreading awareness** and creating educational content. ✅ **Write blogs, guides, and tutorials** explaining how to use Nostr.\ ✅ **Make videos or social media posts** introducing new users to the protocol.\ ✅ **Host discussions, Twitter Spaces, or workshops** to onboard more people. The more people **understand and trust Nostr**, the stronger the ecosystem becomes. --- ## **7️⃣ Support Open-Source Nostr Projects** Many Nostr tools and clients are **built by volunteers**, and open-source projects thrive on **community support**. ✅ **Contribute code** to existing Nostr projects on GitHub.\ ✅ **Report bugs and suggest features** to improve Nostr clients.\ ✅ **Donate to developers** who keep Nostr free and open for everyone. If you're not a developer, you can still **help with testing, translations, and documentation** to make projects more accessible. --- ## **🚀 Every Contribution Strengthens Nostr** Whether you: ✔️ **Post and engage daily**\ ✔️ **Zap creators and developers**\ ✔️ **Run or support relays**\ ✔️ **Build new apps and tools**\ ✔️ **Educate and onboard new users** **Every action helps make Nostr more resilient, decentralized, and unstoppable.** Nostr isn’t just another social network—it’s **a movement toward a free and open internet**. If you believe in **digital freedom, privacy, and decentralization**, now is the time to get involved. @ ae1008d2:a166d760
2025-04-01 00:29:56This is part one in a series of long-form content of my ideas as to what we are entering into in my opinion;*The Roaring '20's 2.0* (working title). I hope you'll join me on this journey together. "*History does not repeat itself, but it often rhymes*"; - Samuel Clemens, aka Mark Twain. My only class I received an A+ in high school was history, this opened up the opportunity for me to enroll in an AP (college level) history class my senior year. There was an inherent nature for me to study history. Another quote I found to live by; "If we do not study history, we are bound to repeat it", a paraphrased quote by the many great philosphers of old from Edmund Burke, George Santayana and even Winston Churchill, all pulling from the same King Solomon quote; "What has been will be again, what has been done will be done again; there is nothing new under the sun". My curiousity of human actions, psychological and therefore economical behavior, has benefitted me greatly throughout my life and career, at such a young age. Being able to 'see around the curves' ahead I thought was a gift many had, but was sorely mistaken. People are just built different. One, if not my hardest action for me is to share. I just do things; act, often without even thinking about writing down or sharing in anyway shape or form what I just did here with friends, what we just built or how we formed these startups, etc., I've finally made the time, mainly for myself, to share my thoughts and ideas as to where we are at, and what we can do moving forward. It's very easy for us living a sovereign-lifestyle in Bitcoin, Nostr and other P2P, cryptographically-signed sovereign tools and tech-stacks alike, permissionless and self-hostable, to take all these tools for granted. We just live with them. Use them everyday. Do you own property? Do you have to take care of the cattle everyday? To live a sovereign life is tough, but most rewarding. As mentioned above, I'm diving into the details in a several part series as to what the roaring '20's were about, how it got to the point it did, and the inevitable outcome we all know what came to be. How does this possibly repeat itself almost exactly a century later? How does Bitcoin play a role? Are we all really going to be replaced by AI robots (again, history rhymes here)? Time will tell, but I think most of us actually using the tools will also forsee many of these possible outcomes, as it's why we are using many of these tools today. The next parts of this series will be released periodically, maybe once per month, maybe once per quarter. I'll also be releasing these on other platforms like Medium for reach, but Nostr will always be first, most important and prioritized. I'll leave you with one of my favorite quotes I've lived by from one of the greatest traders of all time, especially during this roaring '20's era, Jesse Livermore; "Money is made by sitting, not trading".
@ ae1008d2:a166d760
2025-04-01 00:29:56This is part one in a series of long-form content of my ideas as to what we are entering into in my opinion;*The Roaring '20's 2.0* (working title). I hope you'll join me on this journey together. "*History does not repeat itself, but it often rhymes*"; - Samuel Clemens, aka Mark Twain. My only class I received an A+ in high school was history, this opened up the opportunity for me to enroll in an AP (college level) history class my senior year. There was an inherent nature for me to study history. Another quote I found to live by; "If we do not study history, we are bound to repeat it", a paraphrased quote by the many great philosphers of old from Edmund Burke, George Santayana and even Winston Churchill, all pulling from the same King Solomon quote; "What has been will be again, what has been done will be done again; there is nothing new under the sun". My curiousity of human actions, psychological and therefore economical behavior, has benefitted me greatly throughout my life and career, at such a young age. Being able to 'see around the curves' ahead I thought was a gift many had, but was sorely mistaken. People are just built different. One, if not my hardest action for me is to share. I just do things; act, often without even thinking about writing down or sharing in anyway shape or form what I just did here with friends, what we just built or how we formed these startups, etc., I've finally made the time, mainly for myself, to share my thoughts and ideas as to where we are at, and what we can do moving forward. It's very easy for us living a sovereign-lifestyle in Bitcoin, Nostr and other P2P, cryptographically-signed sovereign tools and tech-stacks alike, permissionless and self-hostable, to take all these tools for granted. We just live with them. Use them everyday. Do you own property? Do you have to take care of the cattle everyday? To live a sovereign life is tough, but most rewarding. As mentioned above, I'm diving into the details in a several part series as to what the roaring '20's were about, how it got to the point it did, and the inevitable outcome we all know what came to be. How does this possibly repeat itself almost exactly a century later? How does Bitcoin play a role? Are we all really going to be replaced by AI robots (again, history rhymes here)? Time will tell, but I think most of us actually using the tools will also forsee many of these possible outcomes, as it's why we are using many of these tools today. The next parts of this series will be released periodically, maybe once per month, maybe once per quarter. I'll also be releasing these on other platforms like Medium for reach, but Nostr will always be first, most important and prioritized. I'll leave you with one of my favorite quotes I've lived by from one of the greatest traders of all time, especially during this roaring '20's era, Jesse Livermore; "Money is made by sitting, not trading". @ 5de23b9a:d83005b3
2025-02-19 03:47:19In a digital era that is increasingly controlled by large companies, the emergence of Nostr (Notes and Other Stuff Transmitted by Relays) is a breath of fresh air for those who crave freedom of expression. Nostr is a cryptography-based protocol that allows users to send and receive messages through a relay network. Unlike conventional social media such as Twitter or Facebook 1.Full Decentralization: No company or government can remove or restrict content. 2.Sensor-Resistant: Information remains accessible despite blocking attempts. 3.Privacy and Security: Uses cryptography to ensure that only users who have the keys can access their messages.* **
@ 5de23b9a:d83005b3
2025-02-19 03:47:19In a digital era that is increasingly controlled by large companies, the emergence of Nostr (Notes and Other Stuff Transmitted by Relays) is a breath of fresh air for those who crave freedom of expression. Nostr is a cryptography-based protocol that allows users to send and receive messages through a relay network. Unlike conventional social media such as Twitter or Facebook 1.Full Decentralization: No company or government can remove or restrict content. 2.Sensor-Resistant: Information remains accessible despite blocking attempts. 3.Privacy and Security: Uses cryptography to ensure that only users who have the keys can access their messages.* ** @ ee270b04:7ffc5f0a
2025-03-31 23:00:20<img src="https://blossom.primal.net/8fbf15337001e5094284390fff94d7cadff907a7c5c527729cf262fcd362efa7.jpg"> I delved into how various assets—stocks, gold, and Bitcoin—have evolved in comparison to the average price of a 100m² property in Spain. The findings? Nothing short of fascinating. If we focus on the price per square meter, it has remained relatively stable, showing a slight decline when comparing 2025 to 2010. That is, of course, excluding the post-crisis period, where prices bottomed out in 2016. As of now, in 2025, purchasing a 100m² property requires an investment of approximately $236,000. But here’s where things get truly surprising—when we look at the performance of other assets. Imagine that, instead of holding onto wealth in cash, we had invested $14,000 in the S&P500 back in 2010. Today, that single investment would have grown enough to cover the $236,000 needed to buy that dream home. Now, let’s talk about gold. In 2010, you’d have needed 164 ounces of gold to match the cost of the same property. Fast forward to 2025, and just 75 ounces would do the trick. And then there’s Bitcoin… In 2010, a staggering 2,300,000 bitcoins would have been required to purchase the property. Today, in 2025, you’d only need a mere 2.3 bitcoins.
@ ee270b04:7ffc5f0a
2025-03-31 23:00:20<img src="https://blossom.primal.net/8fbf15337001e5094284390fff94d7cadff907a7c5c527729cf262fcd362efa7.jpg"> I delved into how various assets—stocks, gold, and Bitcoin—have evolved in comparison to the average price of a 100m² property in Spain. The findings? Nothing short of fascinating. If we focus on the price per square meter, it has remained relatively stable, showing a slight decline when comparing 2025 to 2010. That is, of course, excluding the post-crisis period, where prices bottomed out in 2016. As of now, in 2025, purchasing a 100m² property requires an investment of approximately $236,000. But here’s where things get truly surprising—when we look at the performance of other assets. Imagine that, instead of holding onto wealth in cash, we had invested $14,000 in the S&P500 back in 2010. Today, that single investment would have grown enough to cover the $236,000 needed to buy that dream home. Now, let’s talk about gold. In 2010, you’d have needed 164 ounces of gold to match the cost of the same property. Fast forward to 2025, and just 75 ounces would do the trick. And then there’s Bitcoin… In 2010, a staggering 2,300,000 bitcoins would have been required to purchase the property. Today, in 2025, you’d only need a mere 2.3 bitcoins. @ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht: > „Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ > ([Quelle: t.me/rosenbusch/25228](https://t.me/rosenbusch/25228)) Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität. \-- Denn es braucht keinen Untergrund mehr. -- Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür. Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung. Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde. Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen. Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit. Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall.
@ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht: > „Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ > ([Quelle: t.me/rosenbusch/25228](https://t.me/rosenbusch/25228)) Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität. \-- Denn es braucht keinen Untergrund mehr. -- Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür. Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung. Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde. Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen. Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit. Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall. @ 9e69e420:d12360c2
2025-02-17 17:12:01President Trump has intensified immigration enforcement, likening it to a wartime effort. Despite pouring resources into the U.S. Immigration and Customs Enforcement (ICE), arrest numbers are declining and falling short of goals. ICE fell from about 800 daily arrests in late January to fewer than 600 in early February. Critics argue the administration is merely showcasing efforts with ineffectiveness, while Trump seeks billions more in funding to support his deportation agenda. Increased involvement from various federal agencies is intended to assist ICE, but many lack specific immigration training. Challenges persist, as fewer immigrants are available for quick deportation due to a decline in illegal crossings. Local sheriffs are also pressured by rising demands to accommodate immigrants, which may strain resources further.
@ 9e69e420:d12360c2
2025-02-17 17:12:01President Trump has intensified immigration enforcement, likening it to a wartime effort. Despite pouring resources into the U.S. Immigration and Customs Enforcement (ICE), arrest numbers are declining and falling short of goals. ICE fell from about 800 daily arrests in late January to fewer than 600 in early February. Critics argue the administration is merely showcasing efforts with ineffectiveness, while Trump seeks billions more in funding to support his deportation agenda. Increased involvement from various federal agencies is intended to assist ICE, but many lack specific immigration training. Challenges persist, as fewer immigrants are available for quick deportation due to a decline in illegal crossings. Local sheriffs are also pressured by rising demands to accommodate immigrants, which may strain resources further. @ fd208ee8:0fd927c1
2025-02-15 07:02:08E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats". They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable. It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions. What we then have is * a **transaction on a relay** that triggers * a **transaction on a mint** that triggers * a **transaction on Lightning** that triggers * a **transaction on Bitcoin**. Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted. There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself. https://github.com/nostr-protocol/nips/blob/master/60.md
@ fd208ee8:0fd927c1
2025-02-15 07:02:08E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats". They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable. It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions. What we then have is * a **transaction on a relay** that triggers * a **transaction on a mint** that triggers * a **transaction on Lightning** that triggers * a **transaction on Bitcoin**. Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted. There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself. https://github.com/nostr-protocol/nips/blob/master/60.md @ 878dff7c:037d18bc
2025-03-31 21:29:17## Dutton Proposes Easing Home Loan Regulations ### Summary: Opposition Leader Peter Dutton plans to challenge the Albanese government by proposing changes to lending rules aimed at making it easier for first-time home buyers to access loans. The proposed adjustments include reducing serviceability buffers and addressing the treatment of HELP debt to improve housing access. Dutton argues that current regulations create a bias favoring inherited wealth, making it difficult for new buyers to enter the housing market. These proposals come as the Reserve Bank of Australia prepares for its upcoming interest rate decision, with the current cash rate target at 4.1% and predictions of a cut in May. Treasurer Jim Chalmers highlights the government's progress, noting falling inflation, rising real wages, and improving economic growth. Sources: [News.com.au - 1 April 2025](https://www.news.com.au/finance/economy/australian-economy/rba-meets-as-liberals-unveil-help-for-first-home-buyers/news-story/beb22674ff02e2589d1c1ea95ba7cbe5), [The Australian - 1 April 2025](https://www.theaustralian.com.au/nation/politics/election-2025-peter-duttons-bid-to-be-the-new-home-loan-ranger/news-story/733f61adfb16b69e2de97b969afd6c10) ## Australia's Housing Market Hits New Record High ### Summary: Australia's property prices reached a new peak in March, following a rate cut that enhanced buyer optimism. CoreLogic reported a 0.4% monthly increase, bringing the average national property price to A$820,331. All capital cities, except Hobart, experienced price gains, with Sydney and Melbourne rising by 0.3% and 0.5%, respectively. The rate cut slightly improved borrowing capacity and mortgage serviceability. However, the sustainability of this upward trend is uncertain due to persistent affordability issues. While the market rebounded with the February rate cut by the Reserve Bank of Australia, significant improvements in home loan serviceability are necessary for substantial market growth. Source: [Reuters - 1 April 2025](https://www.reuters.com/markets/australia-home-prices-hit-new-record-march-after-rate-cut-corelogic-data-shows-2025-03-31/) ## AI Revolutionizes Business Operations ### Summary: Artificial intelligence (AI) is transforming business practices globally, with applications ranging from administrative task automation to strategic decision-making enhancements. Companies are increasingly integrating AI to streamline operations and gain competitive advantages. This shift necessitates a focus on ethical AI deployment and workforce upskilling to address potential job displacement. Sources: [Financial Times - April 1, 2025](https://www.ft.com/content/2164dc87-f366-48b9-afda-89571a2f4110) ## Criticism of Bureau of Meteorology's Forecasting Capabilities ### Summary: The Bureau of Meteorology is facing criticism for inadequate weather radar coverage in western Queensland, which has led to unreliable forecasting during the recent floods. Federal Opposition Leader Peter Dutton has pledged $10 million for a new radar system to enhance forecasting accuracy, while local officials emphasize the need for improved infrastructure to better prepare for future natural disasters. Sources: [The Australian - April 1, 2025](https://www.theaustralian.com.au/nation/flood-warnings-to-remain-in-queensland-for-months-as-local-mayor-slams-anthony-albanese-for-lack-of-support/news-story/30ae06366e08eb3119116db7a5032541) ## Coalition Pledges $10 Million for Western Queensland Weather Radar ### Summary: As part of the federal election campaign, Opposition Leader Peter Dutton has promised $10 million for a new weather radar system in flood-affected western Queensland. This initiative aims to improve weather forecasting and preparedness in the region. Meanwhile, Prime Minister Anthony Albanese has pledged $200 million for an upgrade to the St John of God Midland hospital in Perth, emphasizing healthcare improvements. Both leaders are focusing on key regional investments as the election approaches. Source: [The Guardian - April 1, 2025](https://www.theguardian.com/australia-news/live/2025/mar/31/election-2025-live-updates-labor-coalition-anthony-albanese-peter-dutton-cost-of-living-nuclear-power-supermarkets-healthcare-ntwnfb) ## Emergency Services Conduct Rescues Amid Queensland Floods ### Summary: Emergency services in Queensland have conducted over 40 rescues as floodwaters continue to rise, submerging communities and causing extensive damage. Efforts are focused on delivering essential supplies, evacuating residents, and ensuring the safety of those affected by the severe weather conditions. Sources: [The Courier-Mail - April 1, 2025](https://www.couriermail.com.au/news/queensland/weather/qld-weather-outback-flooding-to-persist-for-days-if-not-weeks/news-story/2efc920a2a222f2c3156a9c3612e9b2a) ## Six Key Crises Facing Australia Before the Election ### Summary: As the election nears, voters remain largely unaware of six looming crises that could significantly impact the nation. These include over-reliance on volatile commodity exports, challenges in renewable energy implementation, potential currency depreciation, and reduced foreign investment. Both major parties have focused on immediate cost-of-living relief, overshadowing these critical issues that demand urgent attention. Sources: [The Australian - April 1, 2025](https://www.theaustralian.com.au/business/huge-deficit-is-one-of-six-crisis-points-to-know-before-you-vote-in-2025-election/news-story/a4ed4a4cff19e4d574e8ec077f70a291) ## Debate Intensifies Over Australia's Commitment to AUKUS ### Summary: Former Defence Department Secretary Dennis Richardson has urged Australia to persist with the AUKUS submarine agreement despite concerns about the reliability of the U.S. under President Donald Trump. Richardson warns that abandoning the deal now would undermine decades of defense planning. However, critics, including former Prime Minister Malcolm Turnbull, question the feasibility and advisability of the agreement, suggesting alternatives such as partnering with France for submarine development. Sources: [The Guardian - April 1, 2025](https://www.theguardian.com/world/2025/mar/31/dennis-richardson-australia-aukus-submarine-deal-us-former-defence-chief), [The Australian - April 1, 2025](https://www.theaustralian.com.au/nation/defence/former-defence-boss-accuses-malcolm-turnbull-of-undermining-aukus/news-story/eeb5cc35bbb86485bca1fb0eab94efad) ## China Delays $23B Sale of Panama Canal Ports to US-Backed Consortium ### Summary: China has postponed the $23 billion sale of 43 global ports, including critical facilities at both ends of the Panama Canal, to a consortium led by US investment firm BlackRock. The delay follows an investigation by China’s State Administration for Market Regulation into potential anti-monopoly law violations. This unexpected move has heightened tensions between China and the US, as President Trump viewed the sale as a strategic victory in the ongoing power struggle between the two nations. The deal's future remains uncertain, causing political and economic ripples amid China's significant annual "two sessions" gathering. Sources: [New York Post - March 31, 2025](https://nypost.com/2025/03/31/business/china-blocks-23b-sale-of-panama-canal-ports-to-blackrock/) ## Australian Government's Handling of Suspected Chinese Spy Ship Raises Concerns ### Summary: The Australian government has assigned the monitoring of the suspected Chinese spy ship, Tan Suo Yi Hao, to the Australian Border Force, despite Prime Minister Anthony Albanese's assertion that the Australian Defence Force was managing the situation. Security experts believe the vessel is collecting undersea data for future Chinese submarine operations, highlighting national security concerns during an election period. The handling of this issue has led to criticism and confusion over which agency is in charge, with opposition figures condemning the government's lack of detailed information. Sources: [The Australian - April 1, 2025](https://www.theaustralian.com.au/nation/defence/china-spy-ship-has-labor-all-at-sea/news-story/ce46db700a5539daa987ab8c6ab3cb56) ## Concerns Rise Over Schoolchildren Accessing Weight Loss Drugs ### Summary: Health experts are alarmed by reports of Australian schoolchildren accessing weight loss medications like semaglutide (Ozempic) through various means, including online purchases and taking them from home supplies. These substances are being linked to secretive and harmful diet clubs within schools, posing severe health risks such as potentially fatal overdoses. Advocates emphasize the need for stricter regulation of weight loss products and call for mandatory education programs on eating disorders in schools to address the growing issue. Sources: [The Courier-Mail - 1 April 2025](https://www.couriermail.com.au/health/qld-kids-in-deadly-schoolyard-ozempic-diet-clubs/news-story/26463341740be4759df3758eec969225) ## Recycling Plant Explosion Highlights Dangers of Improper Aerosol Disposal ### Summary: A Victorian company has been fined $35,000 after an explosion at its recycling plant injured six workers. The incident occurred when pressurized aerosol cans were improperly shredded, causing flames to spread up to 18 meters. Investigations revealed that the company failed to implement safety procedures such as emptying or puncturing the cans before shredding and ensuring adequate ventilation. This case underscores the critical importance of adhering to safety protocols when handling hazardous materials. Sources: [Herald Sun - 1 April 2025](https://www.heraldsun.com.au/leader/goulburn-valley/rose-and-co-services-fined-after-explosion-injures-six-workers/news-story/bd530692718294843d6fae067bce66ff) ## Australia Enforces New Tobacco Controls from April 1 ### Summary: As of April 1, 2025, Australia has implemented stringent tobacco control measures, including health warnings printed directly on individual cigarettes. These warnings feature phrases such as "CAUSES 16 CANCERS" and "DAMAGES YOUR LUNGS." Additionally, new graphic warnings on cigarette packs and health promotion inserts aim to encourage smoking cessation and raise awareness about the dangers of tobacco use. Sources: [Mirage News - April 1, 2025](https://www.miragenews.com/australia-enforces-new-tobacco-controls-from-1435865/), [9News - April 1, 2025](https://www.9news.com.au/national/health-new-cigarette-warning-in-australia/2c5a5253-eb02-4279-8275-4056dc3f4e76) ## OPEC+ Increases Oil Production Amid Global Uncertainties ### Summary: OPEC+ has announced the gradual unwinding of voluntary production cuts starting April 1, 2025, aiming to restore 2.2 million barrels per day of output by September 2026. Despite this increase, factors such as tighter U.S. sanctions on Iran and Russia, potential sanctions on Venezuelan oil buyers, and fears of a tariff-induced recession have sustained oil prices. Analysts predict limited downside risks to oil prices due to significant supply threats, mainly from Iran and Venezuela. While some strength in oil prices is expected during the summer, concerns over tariff-induced demand weakness persist. Sources: [MarketWatch - April 1, 2025](https://www.marketwatch.com/story/opec-is-boosting-output-in-april-heres-what-that-could-mean-for-oil-prices-940b854b) ## Iconic Australian Locations Declared 'No Go Zones' ### Summary: Several iconic Australian locations, including Uluru, Kakadu National Park, Cape York Peninsula, and others, are increasingly being declared "no go zones" due to cultural, environmental, and safety concerns. These measures aim to preserve the cultural significance and environmental integrity of these landmarks and ensure public safety. While traditional owners and local authorities support these restrictions to protect cultural heritage, debates have arisen over tourists' rights and the impact on local tourism industries. Sources: [News.com.au - April 1, 2025](https://www.news.com.au/travel/travel-updates/warnings/aussie-tourist-destinations-turned-into-no-go-zones/news-story/30d4c803d7cb1e33ef0c50ed72b603b4) ## The Joe Rogan Experience #2297: Francis Foster & Konstantin Kisin ### Summary: In episode #2297 of *The Joe Rogan Experience*, Joe Rogan welcomes comedians and commentators Francis Foster and Konstantin Kisin, hosts of the podcast *Triggernometry*. The episode delivers a wide-ranging conversation covering free speech, comedy, media narratives, and societal tensions in the modern world. **Interesting Discussions and Insights:** - **The State of Comedy:**\ The trio discusses how comedy has changed in recent years, especially under the weight of cancel culture. They explore how comedians are navigating cultural sensitivities while still trying to push boundaries and remain authentic. - **Free Speech and Censorship:**\ Konstantin and Francis share their experiences with censorship and self-censorship, emphasizing the risks of suppressing ideas, even if they’re controversial. They advocate for robust debate as a cornerstone of democracy. - **Migration and Identity Politics:**\ The conversation touches on immigration policies in the UK and broader Western world, discussing how political correctness often silences real concerns. Both guests, with immigrant backgrounds, offer nuanced perspectives on national identity and inclusion. - **Media and Narrative Control:**\ Joe, Francis, and Konstantin dive into how media outlets often frame stories with ideological slants, and the dangers of relying on one-sided narratives in forming public opinion. - **Creating *Triggernometry*:**\ The guests talk about why they launched their podcast — to have honest, open conversations with a wide range of thinkers, especially those often excluded from mainstream platforms. **Key Takeaways:** - Honest conversation is essential for a healthy society, even when it's uncomfortable. - Comedy still holds power to critique society but faces mounting challenges from cultural pressures. - Free speech should be defended not just in principle, but in everyday life and dialogue. - The media landscape is increasingly polarized, and critical thinking is more important than ever. Source: [The Joe Rogan Experience #2297 - Spotify](https://open.spotify.com/episode/5hSnCuPPWsDzq2z8pBWYzD)
@ 878dff7c:037d18bc
2025-03-31 21:29:17## Dutton Proposes Easing Home Loan Regulations ### Summary: Opposition Leader Peter Dutton plans to challenge the Albanese government by proposing changes to lending rules aimed at making it easier for first-time home buyers to access loans. The proposed adjustments include reducing serviceability buffers and addressing the treatment of HELP debt to improve housing access. Dutton argues that current regulations create a bias favoring inherited wealth, making it difficult for new buyers to enter the housing market. These proposals come as the Reserve Bank of Australia prepares for its upcoming interest rate decision, with the current cash rate target at 4.1% and predictions of a cut in May. Treasurer Jim Chalmers highlights the government's progress, noting falling inflation, rising real wages, and improving economic growth. Sources: [News.com.au - 1 April 2025](https://www.news.com.au/finance/economy/australian-economy/rba-meets-as-liberals-unveil-help-for-first-home-buyers/news-story/beb22674ff02e2589d1c1ea95ba7cbe5), [The Australian - 1 April 2025](https://www.theaustralian.com.au/nation/politics/election-2025-peter-duttons-bid-to-be-the-new-home-loan-ranger/news-story/733f61adfb16b69e2de97b969afd6c10) ## Australia's Housing Market Hits New Record High ### Summary: Australia's property prices reached a new peak in March, following a rate cut that enhanced buyer optimism. CoreLogic reported a 0.4% monthly increase, bringing the average national property price to A$820,331. All capital cities, except Hobart, experienced price gains, with Sydney and Melbourne rising by 0.3% and 0.5%, respectively. The rate cut slightly improved borrowing capacity and mortgage serviceability. However, the sustainability of this upward trend is uncertain due to persistent affordability issues. While the market rebounded with the February rate cut by the Reserve Bank of Australia, significant improvements in home loan serviceability are necessary for substantial market growth. Source: [Reuters - 1 April 2025](https://www.reuters.com/markets/australia-home-prices-hit-new-record-march-after-rate-cut-corelogic-data-shows-2025-03-31/) ## AI Revolutionizes Business Operations ### Summary: Artificial intelligence (AI) is transforming business practices globally, with applications ranging from administrative task automation to strategic decision-making enhancements. Companies are increasingly integrating AI to streamline operations and gain competitive advantages. This shift necessitates a focus on ethical AI deployment and workforce upskilling to address potential job displacement. Sources: [Financial Times - April 1, 2025](https://www.ft.com/content/2164dc87-f366-48b9-afda-89571a2f4110) ## Criticism of Bureau of Meteorology's Forecasting Capabilities ### Summary: The Bureau of Meteorology is facing criticism for inadequate weather radar coverage in western Queensland, which has led to unreliable forecasting during the recent floods. Federal Opposition Leader Peter Dutton has pledged $10 million for a new radar system to enhance forecasting accuracy, while local officials emphasize the need for improved infrastructure to better prepare for future natural disasters. Sources: [The Australian - April 1, 2025](https://www.theaustralian.com.au/nation/flood-warnings-to-remain-in-queensland-for-months-as-local-mayor-slams-anthony-albanese-for-lack-of-support/news-story/30ae06366e08eb3119116db7a5032541) ## Coalition Pledges $10 Million for Western Queensland Weather Radar ### Summary: As part of the federal election campaign, Opposition Leader Peter Dutton has promised $10 million for a new weather radar system in flood-affected western Queensland. This initiative aims to improve weather forecasting and preparedness in the region. Meanwhile, Prime Minister Anthony Albanese has pledged $200 million for an upgrade to the St John of God Midland hospital in Perth, emphasizing healthcare improvements. Both leaders are focusing on key regional investments as the election approaches. Source: [The Guardian - April 1, 2025](https://www.theguardian.com/australia-news/live/2025/mar/31/election-2025-live-updates-labor-coalition-anthony-albanese-peter-dutton-cost-of-living-nuclear-power-supermarkets-healthcare-ntwnfb) ## Emergency Services Conduct Rescues Amid Queensland Floods ### Summary: Emergency services in Queensland have conducted over 40 rescues as floodwaters continue to rise, submerging communities and causing extensive damage. Efforts are focused on delivering essential supplies, evacuating residents, and ensuring the safety of those affected by the severe weather conditions. Sources: [The Courier-Mail - April 1, 2025](https://www.couriermail.com.au/news/queensland/weather/qld-weather-outback-flooding-to-persist-for-days-if-not-weeks/news-story/2efc920a2a222f2c3156a9c3612e9b2a) ## Six Key Crises Facing Australia Before the Election ### Summary: As the election nears, voters remain largely unaware of six looming crises that could significantly impact the nation. These include over-reliance on volatile commodity exports, challenges in renewable energy implementation, potential currency depreciation, and reduced foreign investment. Both major parties have focused on immediate cost-of-living relief, overshadowing these critical issues that demand urgent attention. Sources: [The Australian - April 1, 2025](https://www.theaustralian.com.au/business/huge-deficit-is-one-of-six-crisis-points-to-know-before-you-vote-in-2025-election/news-story/a4ed4a4cff19e4d574e8ec077f70a291) ## Debate Intensifies Over Australia's Commitment to AUKUS ### Summary: Former Defence Department Secretary Dennis Richardson has urged Australia to persist with the AUKUS submarine agreement despite concerns about the reliability of the U.S. under President Donald Trump. Richardson warns that abandoning the deal now would undermine decades of defense planning. However, critics, including former Prime Minister Malcolm Turnbull, question the feasibility and advisability of the agreement, suggesting alternatives such as partnering with France for submarine development. Sources: [The Guardian - April 1, 2025](https://www.theguardian.com/world/2025/mar/31/dennis-richardson-australia-aukus-submarine-deal-us-former-defence-chief), [The Australian - April 1, 2025](https://www.theaustralian.com.au/nation/defence/former-defence-boss-accuses-malcolm-turnbull-of-undermining-aukus/news-story/eeb5cc35bbb86485bca1fb0eab94efad) ## China Delays $23B Sale of Panama Canal Ports to US-Backed Consortium ### Summary: China has postponed the $23 billion sale of 43 global ports, including critical facilities at both ends of the Panama Canal, to a consortium led by US investment firm BlackRock. The delay follows an investigation by China’s State Administration for Market Regulation into potential anti-monopoly law violations. This unexpected move has heightened tensions between China and the US, as President Trump viewed the sale as a strategic victory in the ongoing power struggle between the two nations. The deal's future remains uncertain, causing political and economic ripples amid China's significant annual "two sessions" gathering. Sources: [New York Post - March 31, 2025](https://nypost.com/2025/03/31/business/china-blocks-23b-sale-of-panama-canal-ports-to-blackrock/) ## Australian Government's Handling of Suspected Chinese Spy Ship Raises Concerns ### Summary: The Australian government has assigned the monitoring of the suspected Chinese spy ship, Tan Suo Yi Hao, to the Australian Border Force, despite Prime Minister Anthony Albanese's assertion that the Australian Defence Force was managing the situation. Security experts believe the vessel is collecting undersea data for future Chinese submarine operations, highlighting national security concerns during an election period. The handling of this issue has led to criticism and confusion over which agency is in charge, with opposition figures condemning the government's lack of detailed information. Sources: [The Australian - April 1, 2025](https://www.theaustralian.com.au/nation/defence/china-spy-ship-has-labor-all-at-sea/news-story/ce46db700a5539daa987ab8c6ab3cb56) ## Concerns Rise Over Schoolchildren Accessing Weight Loss Drugs ### Summary: Health experts are alarmed by reports of Australian schoolchildren accessing weight loss medications like semaglutide (Ozempic) through various means, including online purchases and taking them from home supplies. These substances are being linked to secretive and harmful diet clubs within schools, posing severe health risks such as potentially fatal overdoses. Advocates emphasize the need for stricter regulation of weight loss products and call for mandatory education programs on eating disorders in schools to address the growing issue. Sources: [The Courier-Mail - 1 April 2025](https://www.couriermail.com.au/health/qld-kids-in-deadly-schoolyard-ozempic-diet-clubs/news-story/26463341740be4759df3758eec969225) ## Recycling Plant Explosion Highlights Dangers of Improper Aerosol Disposal ### Summary: A Victorian company has been fined $35,000 after an explosion at its recycling plant injured six workers. The incident occurred when pressurized aerosol cans were improperly shredded, causing flames to spread up to 18 meters. Investigations revealed that the company failed to implement safety procedures such as emptying or puncturing the cans before shredding and ensuring adequate ventilation. This case underscores the critical importance of adhering to safety protocols when handling hazardous materials. Sources: [Herald Sun - 1 April 2025](https://www.heraldsun.com.au/leader/goulburn-valley/rose-and-co-services-fined-after-explosion-injures-six-workers/news-story/bd530692718294843d6fae067bce66ff) ## Australia Enforces New Tobacco Controls from April 1 ### Summary: As of April 1, 2025, Australia has implemented stringent tobacco control measures, including health warnings printed directly on individual cigarettes. These warnings feature phrases such as "CAUSES 16 CANCERS" and "DAMAGES YOUR LUNGS." Additionally, new graphic warnings on cigarette packs and health promotion inserts aim to encourage smoking cessation and raise awareness about the dangers of tobacco use. Sources: [Mirage News - April 1, 2025](https://www.miragenews.com/australia-enforces-new-tobacco-controls-from-1435865/), [9News - April 1, 2025](https://www.9news.com.au/national/health-new-cigarette-warning-in-australia/2c5a5253-eb02-4279-8275-4056dc3f4e76) ## OPEC+ Increases Oil Production Amid Global Uncertainties ### Summary: OPEC+ has announced the gradual unwinding of voluntary production cuts starting April 1, 2025, aiming to restore 2.2 million barrels per day of output by September 2026. Despite this increase, factors such as tighter U.S. sanctions on Iran and Russia, potential sanctions on Venezuelan oil buyers, and fears of a tariff-induced recession have sustained oil prices. Analysts predict limited downside risks to oil prices due to significant supply threats, mainly from Iran and Venezuela. While some strength in oil prices is expected during the summer, concerns over tariff-induced demand weakness persist. Sources: [MarketWatch - April 1, 2025](https://www.marketwatch.com/story/opec-is-boosting-output-in-april-heres-what-that-could-mean-for-oil-prices-940b854b) ## Iconic Australian Locations Declared 'No Go Zones' ### Summary: Several iconic Australian locations, including Uluru, Kakadu National Park, Cape York Peninsula, and others, are increasingly being declared "no go zones" due to cultural, environmental, and safety concerns. These measures aim to preserve the cultural significance and environmental integrity of these landmarks and ensure public safety. While traditional owners and local authorities support these restrictions to protect cultural heritage, debates have arisen over tourists' rights and the impact on local tourism industries. Sources: [News.com.au - April 1, 2025](https://www.news.com.au/travel/travel-updates/warnings/aussie-tourist-destinations-turned-into-no-go-zones/news-story/30d4c803d7cb1e33ef0c50ed72b603b4) ## The Joe Rogan Experience #2297: Francis Foster & Konstantin Kisin ### Summary: In episode #2297 of *The Joe Rogan Experience*, Joe Rogan welcomes comedians and commentators Francis Foster and Konstantin Kisin, hosts of the podcast *Triggernometry*. The episode delivers a wide-ranging conversation covering free speech, comedy, media narratives, and societal tensions in the modern world. **Interesting Discussions and Insights:** - **The State of Comedy:**\ The trio discusses how comedy has changed in recent years, especially under the weight of cancel culture. They explore how comedians are navigating cultural sensitivities while still trying to push boundaries and remain authentic. - **Free Speech and Censorship:**\ Konstantin and Francis share their experiences with censorship and self-censorship, emphasizing the risks of suppressing ideas, even if they’re controversial. They advocate for robust debate as a cornerstone of democracy. - **Migration and Identity Politics:**\ The conversation touches on immigration policies in the UK and broader Western world, discussing how political correctness often silences real concerns. Both guests, with immigrant backgrounds, offer nuanced perspectives on national identity and inclusion. - **Media and Narrative Control:**\ Joe, Francis, and Konstantin dive into how media outlets often frame stories with ideological slants, and the dangers of relying on one-sided narratives in forming public opinion. - **Creating *Triggernometry*:**\ The guests talk about why they launched their podcast — to have honest, open conversations with a wide range of thinkers, especially those often excluded from mainstream platforms. **Key Takeaways:** - Honest conversation is essential for a healthy society, even when it's uncomfortable. - Comedy still holds power to critique society but faces mounting challenges from cultural pressures. - Free speech should be defended not just in principle, but in everyday life and dialogue. - The media landscape is increasingly polarized, and critical thinking is more important than ever. Source: [The Joe Rogan Experience #2297 - Spotify](https://open.spotify.com/episode/5hSnCuPPWsDzq2z8pBWYzD) @ 0fa80bd3:ea7325de
2025-02-14 23:24:37#intro The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises. In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously. I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea. It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope. After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes. I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project. With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed. With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation. At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
@ 0fa80bd3:ea7325de
2025-02-14 23:24:37#intro The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises. In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously. I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea. It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope. After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes. I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project. With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed. With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation. At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project. @ f3873798:24b3f2f3
2025-03-31 20:14:31Olá, nostrilianos! O tema de hoje é inteligência artificial (IA), com foco em duas ferramentas que têm se destacado no mercado por sua capacidade de responder perguntas, auxiliar em tarefas e, em alguns casos, até gerar imagens. Essas tecnologias estão cada vez mais presentes no dia a dia, ajudando desde a correção de textos até pesquisas rápidas e a criação de imagens personalizadas com base em prompts específicos. Nesse cenário em expansão, duas IAs se sobressaem: o ChatGPT, desenvolvido pela OpenAI, e o Grok, criado pela xAI. Ambas são ferramentas poderosas, cada uma com seus pontos fortes e limitações, e têm conquistado usuários ao redor do mundo. Neste artigo, compartilho minhas impressões sobre essas duas IAs, baseadas em minha experiência pessoal, destacando suas diferenças e vantagens. ### Grok: Destaque na criação de imagens e fontes  O Grok me impressiona especialmente em dois aspectos. Primeiro, sua capacidade de gerar imagens é um diferencial significativo. Enquanto o ChatGPT tem limitações nesse quesito, o Grok oferece uma funcionalidade mais robusta para criar visuais únicos a partir de prompts, o que pode ser uma vantagem para quem busca criatividade visual. Segundo, o Grok frequentemente cita fontes ou indica a origem das informações que fornece, o que agrega credibilidade às suas respostas e facilita a verificação dos dados. ### ChatGPT: Assertividade e clareza  Por outro lado, o ChatGPT se destaca pela assertividade e pela clareza em suas explicações. Suas respostas tendem a ser mais diretas e concisas, o que é ideal para quem busca soluções rápidas ou explicações objetivas. Acredito que essa vantagem possa estar ligada ao fato de o ChatGPT estar em operação há mais tempo, tendo passado por anos de aprimoramento e ajustes com base em interações de usuários.Comparação e reflexões. Em minha experiência, o Grok supera o ChatGPT na geração de imagens e na citação de fontes, enquanto o ChatGPT leva a melhor em precisão e simplicidade nas respostas. Esses pontos refletem não apenas as prioridades de design de cada IA, mas também o tempo de desenvolvimento e os objetivos de suas respectivas empresas criadoras. A OpenAI, por trás do ChatGPT, focou em refinamento conversacional, enquanto a xAI, com o Grok, parece investir em funcionalidades adicionais, como a criação de conteúdo visual. ### Minha opinião  Não há um vencedor absoluto entre Grok e ChatGPT – a escolha depende do que você precisa. Se seu foco é geração de imagens ou rastreamento de fontes, o Grok pode ser a melhor opção. Se busca respostas rápidas e assertivas, o ChatGPT provavelmente atenderá melhor. Ambas as IAs são ferramentas incríveis, e o mais fascinante é ver como elas continuam evoluindo, moldando o futuro da interação entre humanos e máquinas.
@ f3873798:24b3f2f3
2025-03-31 20:14:31Olá, nostrilianos! O tema de hoje é inteligência artificial (IA), com foco em duas ferramentas que têm se destacado no mercado por sua capacidade de responder perguntas, auxiliar em tarefas e, em alguns casos, até gerar imagens. Essas tecnologias estão cada vez mais presentes no dia a dia, ajudando desde a correção de textos até pesquisas rápidas e a criação de imagens personalizadas com base em prompts específicos. Nesse cenário em expansão, duas IAs se sobressaem: o ChatGPT, desenvolvido pela OpenAI, e o Grok, criado pela xAI. Ambas são ferramentas poderosas, cada uma com seus pontos fortes e limitações, e têm conquistado usuários ao redor do mundo. Neste artigo, compartilho minhas impressões sobre essas duas IAs, baseadas em minha experiência pessoal, destacando suas diferenças e vantagens. ### Grok: Destaque na criação de imagens e fontes  O Grok me impressiona especialmente em dois aspectos. Primeiro, sua capacidade de gerar imagens é um diferencial significativo. Enquanto o ChatGPT tem limitações nesse quesito, o Grok oferece uma funcionalidade mais robusta para criar visuais únicos a partir de prompts, o que pode ser uma vantagem para quem busca criatividade visual. Segundo, o Grok frequentemente cita fontes ou indica a origem das informações que fornece, o que agrega credibilidade às suas respostas e facilita a verificação dos dados. ### ChatGPT: Assertividade e clareza  Por outro lado, o ChatGPT se destaca pela assertividade e pela clareza em suas explicações. Suas respostas tendem a ser mais diretas e concisas, o que é ideal para quem busca soluções rápidas ou explicações objetivas. Acredito que essa vantagem possa estar ligada ao fato de o ChatGPT estar em operação há mais tempo, tendo passado por anos de aprimoramento e ajustes com base em interações de usuários.Comparação e reflexões. Em minha experiência, o Grok supera o ChatGPT na geração de imagens e na citação de fontes, enquanto o ChatGPT leva a melhor em precisão e simplicidade nas respostas. Esses pontos refletem não apenas as prioridades de design de cada IA, mas também o tempo de desenvolvimento e os objetivos de suas respectivas empresas criadoras. A OpenAI, por trás do ChatGPT, focou em refinamento conversacional, enquanto a xAI, com o Grok, parece investir em funcionalidades adicionais, como a criação de conteúdo visual. ### Minha opinião  Não há um vencedor absoluto entre Grok e ChatGPT – a escolha depende do que você precisa. Se seu foco é geração de imagens ou rastreamento de fontes, o Grok pode ser a melhor opção. Se busca respostas rápidas e assertivas, o ChatGPT provavelmente atenderá melhor. Ambas as IAs são ferramentas incríveis, e o mais fascinante é ver como elas continuam evoluindo, moldando o futuro da interação entre humanos e máquinas. @ 9e69e420:d12360c2
2025-02-14 18:07:10Vice President J.D. Vance addressed the Munich Security Conference, criticizing European leaders for undermining free speech and traditional values. He claimed that the biggest threat to Europe is not from external enemies but from internal challenges. Vance condemned the arrest of a British man for praying near an abortion clinic and accused European politicians of censorship. He urged leaders to combat illegal immigration and questioned their democratic practices. “There is a new sheriff in town,” he said, referring to President Trump. Vance's remarks were unexpected, as many anticipated discussions on security or Ukraine. His speech emphasized the need for Europe to share the defense burden to ensure stability and security.
@ 9e69e420:d12360c2
2025-02-14 18:07:10Vice President J.D. Vance addressed the Munich Security Conference, criticizing European leaders for undermining free speech and traditional values. He claimed that the biggest threat to Europe is not from external enemies but from internal challenges. Vance condemned the arrest of a British man for praying near an abortion clinic and accused European politicians of censorship. He urged leaders to combat illegal immigration and questioned their democratic practices. “There is a new sheriff in town,” he said, referring to President Trump. Vance's remarks were unexpected, as many anticipated discussions on security or Ukraine. His speech emphasized the need for Europe to share the defense burden to ensure stability and security. @ 866e0139:6a9334e5
2025-03-31 19:38:39  *** **Autor:** **[Carlos A. Gebauer.](https://make-love-not-law.com/lebenslauf.html)** *Dieser Beitrag wurde mit dem **[Pareto-Client](https://pareto.space/read)** geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden **[hier.](https://pareto.space/read?category=friedenstaube)*** *** Am 18. März 1924 schenkte meine Großmutter ihren Töchtern einen kleinen Bruder. Weil sein Vater fürchtete, der Junge könnte unter seinen vier Schwestern verweichlichen, schickte er den Kleinen zu Wochenendfreizeiten einer örtlichen Pfadfindergruppe. Ein Weltkriegsveteran veranstaltete dort mit den Kindern Geländespiele quer durch die schlesischen Wälder. Man lernte, Essbares zu finden, Pilze zu bestimmen, sich im Freien zu orientieren und Feuer zu machen. Bald wurde deutlich, dass der Heranwachsende auch nicht mehr in den Blockflötenkreis seiner Schwestern und ihrer Freundinnen passte. Das Umfeld befürwortete, sein besonderes musikalisches Talent auf das Klavierspiel und das Flügelhorn zu richten. Kontakte bei der anschließenden Kirchenmusik mündeten schließlich in den elterlichen Entschluss, den nun 14-jährigen in ein Musikschulinternat zu schicken. ### Es begann der Zweite Weltkrieg Ein Jahr später, das erste Heimweh hatte sich langsam beruhigt, änderten sich die Verhältnisse schlagartig. Es begann der Zweite Weltkrieg. Mitschüler unter den jungen Musikern erfuhren, dass ihre älteren Brüder nun Soldaten werden mussten. Noch hielt sich die Gemeinschaft der jetzt 15-jährigen im Internat aber an einer Hoffnung fest: Bis sie selbst in das wehrfähige Alter kommen würden, müsste der Krieg längst beendet sein. In dieser Stimmungslage setzten sie ihre Ausbildung fort. Es kam anders. Für den 18-jährigen erfolgte die befürchtete Einberufung in Form des „Gestellungsbefehls“. Entsprechend seiner Fähigkeiten sah man ihn zunächst für ein Musikkorps vor und schickte ihn zu einer ersten Grundausbildung nach Südfrankreich. Bei Nizza fand er sich nun plötzlich zwischen Soldaten, die Handgranaten in das Mittelmeer warfen, um Fische zu fangen. Es war das erste Mal, dass er fürchtete, infolge Explosionslärms sein Gehör zu verlieren. In den kommenden Jahren sollte er oft die Ohren zu- und den Mund offenhalten müssen, um sich wenigstens die Möglichkeit der angezielten Berufsausübung zu erhalten – wenn es überhaupt je dazu kommen würde. *** **DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!** ***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos* ***[hier](https://pareto.space/a/naddr1qqsxydty8qek2wpsvyck2wphxajrvefjvesngcfhxenrgdty89nrzvgzyzrxuqfepp2e79w9aluaz2252vyz7qdpld05pgjmeurhdgm2jv6w2qcyqqq823cpp4mhxue69uhkummn9ekx7mqprpmhxue69uhkummnw3ezuurpwfjhgmewwdcxzcm9qythwumn8ghj7mn0wd68ytnsv9ex2ar09e6x7amwqyf8wumn8ghj7mmxve3ksctfdch8qatzqythwumn8ghj7urpwfjhgmewdehhxarjxyhxxmmdszcvqk)*** *oder am Ende des Textes.* *** Schon nach kurzer Zeit änderte sich die Befehlslage wieder. Der Musikstudent wurde nun zum Infanteristen und nach Russland an die Front verbracht. Vor ihm lagen jetzt drei Kriegsjahre: Gewalt, Dreck, Gewehrkugeln, Panzerschlachten, Granatsplitter, Luftangriffe, Entbehrungen, Hunger, Kälte, sieben Verwundungen, Blut und Schmerzen, Sterbende überall, Tote, Schreiende. Verzweiflung. Sorgen. Ängste. Todesangst. Zurückweichen? Verboten! Und die stets klare Ansage dazu: Wer nicht da vorne gegen den Feind um sein Leben kämpft, dem wird es ganz sicher da hinten von den eigenen Kameraden genommen. Ein gewährter Fronturlaub 1944 versprach glückliche Momente. Zurück zu den Eltern, zurück zu den Schwestern, zurück nach Freiburg. Doch die Familie war nicht zu Hause, die Türen verschlossen. Eine Nachbarin öffnete ihr Fenster und rief dem Ratlosen zu: „Beeil‘ dich! Renn‘ zum Friedhof. Der Vater ist tot. Sie sind alle bei der Beerdigung!“ Wieder hieß es, qualvoll Abschied nehmen. Zurück an die Front. Nach einem weiteren russischen Winter brach sich unübersehbar die Erkenntnis Bahn, dass der Krieg nun seinem Ende zugehe. Doch das Bemühen im Rückzug, sich mit einem versprengten Haufen irgendwie Richtung Heimat orientieren zu können, wurde doppelt jäh unterbrochen. Fanatische Vorgesetzte befahlen die längst Geschlagenen wieder gen Osten. Kurz darauf fielen sie heranrückenden russischen Truppen in die Hände. ### Kriegsgefangenschaft: Tabakration gegen Brot Drei Jahre dem Tod entgangen, schwer verletzt und erschöpft war der 21-jährige also nun ein Kriegsgefangener. Jetzt lagen drei Jahre russischer Kriegsgefangenschaft vor ihm. Ständig war unklar, wie es weiterginge. Unmöglich jedenfalls, sich noch wie ein Pfadfinder aus den Wäldern zu ernähren. Es begannen die Jahre des Schlafens auf Brettern, die Zeit der ziellosen Zugtransporte an unbekannte Orte. Niemand sprach. Nur der Sonnenstand machte klar: Es ging nie Richtung Heimat, sondern immer weiter nach Osten. Weil der Blechbläser nicht rauchte, konnte er seine Tabakration gegen Brot tauschen. So überlebte er auch die Zeit des Hungers und der Morde in den Lagern, die Horrorbilder der nachts Erschlagenen und in die Latrinen geworfenen Toten, der sinnlosen Zwangsarbeiten und der allgegenwärtigen Wanzen. Wer versuchte zu fliehen, der wurde erschossen und sein Körper zur Abschreckung in den Fangdrähten belassen. Im Sommer stanken die dort verwesenden Leichen, wenn nicht Vögel sie rechtzeitig gefressen hatten. Als der 24-jährige schließlich sechs Jahre nach seiner Einberufung aus russischer Kriegsgefangenschaft entlassen wurde, gab es kein Zurück mehr in seine schlesische Heimat. Abgemagert reiste er der vertriebenen Mutter nach, die mit seinen Schwestern und Millionen anderen Flüchtlingen im Westen Deutschlands verteilt worden war. Kraft Ordnungsverfügung wohnte sie jetzt im sauerländischen Bad Laasphe in einem schimmligen Garagenanbau. Als ihn ein Passant auf dieser Reise morgens allein, nur mit einem Becher an der Schnur um den Hals, auf Krücken durch Berlin ziehen sah, gab er ihm schweigend sein Butterbrot. Der kleine, sanfte Junge aus dem schlesischen Freiburg hat danach noch 60 Jahre gelebt. Es dauerte zunächst sechs Jahre, bis er wieder kräftig genug war, ein Instrument zu spielen. 30-jährig saß er dann endlich in einem Orchester und begann ein normales Berufsleben. Aber sein Körper und seine Seele waren für immer aus jeder Normalität gerissen. Irgendwo in Russland war ihm die linke Hüfte so versteift worden, dass sich seine Beine im Liegen an Wade und Schienbein überkreuzten. Er musste also stets den Oberkörper vorbeugen, um überhaupt laufen zu können. Über die Jahrzehnte verzog sich so sein gesamter Knochenbau. Jeder Tag brachte neue orthopädische Probleme und Schmerzen. Ärzte, Masseure, Physiotherapeuten, Schmerzmittel und Spezialausrüstungen aller Art prägten die Tagesabläufe. Asymmetrisch standen seine Schuhe nebeneinander, die ein Spezialschuster ihm mit erhöhter Sohle und Seitenstabilisierung am Knöchel fertigte. Sessel oder Sofas waren ihm nicht nutzbar, da er nur auf einem Spezialstuhl mit halb abgesenkter Sitzfläche Ruhe fand. Auf fremden Stühlen konnte er nur deren Vorderkante nutzen. ### "In den Nächten schrie er im Schlaf" Und auch wenn er sich ohne Krankheitstage bis zuletzt durch seinen Berufsalltag kämpfte, so gab es doch viele Tage voller entsetzlicher Schmerzen, wenn sich seine verdrehte Wirbelsäule zur Migräne in den Kopf bohrte. Bei alledem hörte man ihn allerdings niemals über sein Schicksal klagen. Er ertrug den ganzen Wahnsinn mit einer unbeschreiblichen Duldsamkeit. Nur in den Nächten schrie er bisweilen im Schlaf. In einem seiner Alpträume fürchtete er, Menschen getötet zu haben. Aber auch das erzählte er jahrzehntelang einzig seiner Frau. Als sich einige Jahre vor seinem Tod der orthopädische Zustand weiter verschlechterte, konsultierte er einen Operateur, um Entlastungsmöglichkeiten zu erörtern. Der legte ihn auf eine Untersuchungsliege und empfahl, Verbesserungsversuche zu unterlassen, weil sie die Lage allenfalls verschlechtern konnten. In dem Moment, als er sich von der Liege erheben sollte, wurde deutlich, dass ihm dies nicht gelang. Die gereichte Hand, um ihn hochzuziehen, ignorierte er. Stattdessen rieb er seinen Rumpf ganz alleine eine quälend lange Minute über die Fläche, bis er endlich einen Winkel fand, um sich selbst in die Senkrechte zu bugsieren. Sich nicht auf andere verlassen, war sein Überlebenskonzept. Jahre später, als sich sein Zustand noch weiter verschlechtert hatte, lächelte er über seine Behinderung: „Ich hätte schon vor 60 Jahren tot auf einem Acker in Russland liegen können.“ Alles gehe irgendwann vorbei, tröstete er sich. Das war das andere Überlebenskonzept: liebevoll, friedfertig und sanft anderen gegenüber, unerbittlich mit sich selbst. Sechs Monate vor seinem Tod saß er morgens regungslos auf seinem Spezialstuhl. Eine Altenpflegerin fand ihn und schlug Alarm. Mit allen Kunstgriffen der medizinischen Technik wurde er noch einmal in das Leben zurückkatapultiert. Aber seine Kräfte waren erschöpft. Es schob sich das Grauen der Vergangenheit zwischen ihn und die Welt. Bettlägerig kreiste er um sich selbst, erkannte niemanden und starrte mit weit offenen Augen an die Decke. „Die Russen schmeißen wieder Brandbomben!“, war einer seiner letzten Sätze. Der kleine Junge aus Schlesien ist nicht zu weich geraten. Er hat sein Leid mit unbeugsamer Duldsamkeit ertragen. Er trug es wohl als Strafe für das Leid, das er anderen anzutun genötigt worden war. An seinem Geburtstag blühen immer die Magnolien. In diesem Jahr zum hundertsten Mal. *Dieser Text wurde am 23.3.2024 erstveröffentlicht auf* *[„eigentümlich frei“.](https://ef-magazin.de/2024/03/23/21072-make-love-not-law-kriegstuechtig)* *** *Carlos A. Gebauer studierte Philosophie, Neuere Geschichte, Sprach-, Rechts- und Musikwissenschaften in Düsseldorf, Bayreuth und Bonn. Sein juristisches Referendariat absolvierte er in Düsseldorf, u.a. mit Wahlstationen bei der Landesrundfunkanstalt NRW, bei der Spezialkammer für Kassenarztrecht des Sozialgerichtes Düsseldorf und bei dem Gnadenbeauftragten der Staatsanwaltschaft Düsseldorf.* *Er war unter anderem als Rechtsanwalt und Notarvertreter bis er im November 2003 vom nordrhein-westfälischen Justizministerium zum Richter am Anwaltsgericht für den Bezirk der Rechtsanwaltskammer Düsseldorf ernannt wurde. Seit April 2012 arbeitet er in der Düsseldorfer Rechtsanwaltskanzlei Lindenau, Prior & Partner. Im Juni 2015 wählte ihn die Friedrich-August-von-Hayek-Gesellschaft zu ihrem Stellvertretenden Vorsitzenden. Seit Dezember 2015 ist er Richter im Zweiten Senat des Anwaltsgerichtshofes NRW.* *1995 hatte er parallel zu seiner anwaltlichen Tätigkeit mit dem Verfassen gesellschaftspolitischer und juristischer Texte begonnen. Diese erschienen seither unter anderem in der Neuen Juristischen Wochenschrift (NJW), der Zeitschrift für Rechtspolitik (ZRP) in der [Frankfurter Allgemeinen Zeitung](http://www.faz.de/), der [Freien Presse Chemnitz](http://www.freiepresse.de/), dem „Schweizer Monat“ oder dem Magazin für politische Kultur CICERO. Seit dem Jahr 2005 ist Gebauer ständiger Kolumnist und Autor des Magazins „eigentümlich frei“.* *Gebauer glaubt als puristischer Liberaler unverbrüchlich an die sittliche Verpflichtung eines jeden einzelnen, sein Leben für sich selbst und für seine Mitmenschen verantwortlich zu gestalten; jede Fremdbestimmung durch Gesetze, staatliche Verwaltung, politischen Einfluss oder sonstige Gewalteinwirkung hat sich demnach auf ein ethisch vertretbares Minimum zu beschränken. Die Vorstellung eines europäischen Bundesstaates mit zentral detailsteuernder, supranationaler Staatsgewalt hält er für absurd und verfassungswidrig.* \ **Aktuelle Bücher:** Hayeks Warnung vor der Knechtschaft (2024) – [hier im Handel](https://www.buchkomplizen.de/hayeks-warnung-vor-der-knechtschaft.html?listtype=search\&searchparam=Carlos%2520A%2520gebauer) Das Prinzip Verantwortungslosigkeit (2023) – [hier im Handel](https://www.buchkomplizen.de/das-prinzip-verantwortungslosigkeit.html?listtype=search\&searchparam=Carlos%2520A%2520gebauer) *** **LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!** ***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.* Schon jetzt können Sie uns unterstützen: * Für **50 CHF/EURO** bekommen Sie ein Jahresabo der Friedenstaube. * Für **120 CHF/EURO** bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube. * Für **500 CHF/EURO** werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube. * Ab **1000 CHF** werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie). **Für Einzahlungen in CHF (Betreff: Friedenstaube):** 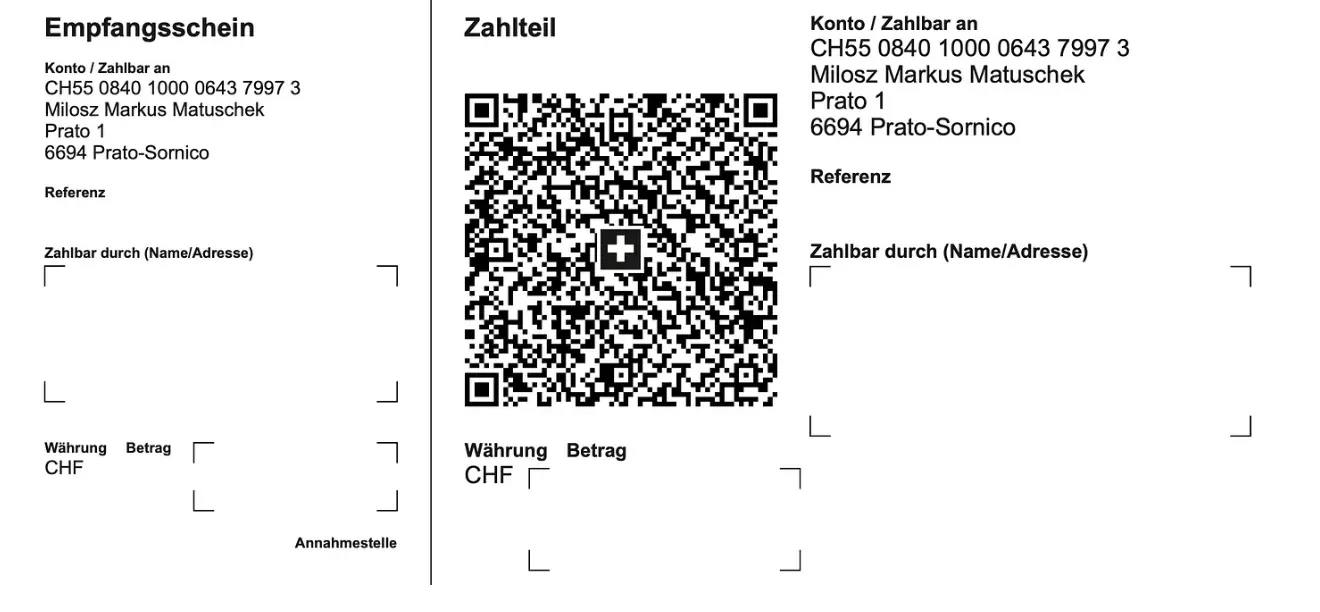 **Für Einzahlungen in Euro:** Milosz Matuschek IBAN DE 53710520500000814137 BYLADEM1TST Sparkasse Traunstein-Trostberg **Betreff: Friedenstaube** Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: <milosz@pareto.space> *** **Sie sind noch nicht auf** [Nostr](https://nostr.com/) **and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil!** Erstellen Sie sich einen Account auf [Start.](https://start.njump.me/) Weitere Onboarding-Leitfäden gibt es im [Pareto-Wiki.](https://wiki.pareto.space/de/home)
@ 866e0139:6a9334e5
2025-03-31 19:38:39  *** **Autor:** **[Carlos A. Gebauer.](https://make-love-not-law.com/lebenslauf.html)** *Dieser Beitrag wurde mit dem **[Pareto-Client](https://pareto.space/read)** geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden **[hier.](https://pareto.space/read?category=friedenstaube)*** *** Am 18. März 1924 schenkte meine Großmutter ihren Töchtern einen kleinen Bruder. Weil sein Vater fürchtete, der Junge könnte unter seinen vier Schwestern verweichlichen, schickte er den Kleinen zu Wochenendfreizeiten einer örtlichen Pfadfindergruppe. Ein Weltkriegsveteran veranstaltete dort mit den Kindern Geländespiele quer durch die schlesischen Wälder. Man lernte, Essbares zu finden, Pilze zu bestimmen, sich im Freien zu orientieren und Feuer zu machen. Bald wurde deutlich, dass der Heranwachsende auch nicht mehr in den Blockflötenkreis seiner Schwestern und ihrer Freundinnen passte. Das Umfeld befürwortete, sein besonderes musikalisches Talent auf das Klavierspiel und das Flügelhorn zu richten. Kontakte bei der anschließenden Kirchenmusik mündeten schließlich in den elterlichen Entschluss, den nun 14-jährigen in ein Musikschulinternat zu schicken. ### Es begann der Zweite Weltkrieg Ein Jahr später, das erste Heimweh hatte sich langsam beruhigt, änderten sich die Verhältnisse schlagartig. Es begann der Zweite Weltkrieg. Mitschüler unter den jungen Musikern erfuhren, dass ihre älteren Brüder nun Soldaten werden mussten. Noch hielt sich die Gemeinschaft der jetzt 15-jährigen im Internat aber an einer Hoffnung fest: Bis sie selbst in das wehrfähige Alter kommen würden, müsste der Krieg längst beendet sein. In dieser Stimmungslage setzten sie ihre Ausbildung fort. Es kam anders. Für den 18-jährigen erfolgte die befürchtete Einberufung in Form des „Gestellungsbefehls“. Entsprechend seiner Fähigkeiten sah man ihn zunächst für ein Musikkorps vor und schickte ihn zu einer ersten Grundausbildung nach Südfrankreich. Bei Nizza fand er sich nun plötzlich zwischen Soldaten, die Handgranaten in das Mittelmeer warfen, um Fische zu fangen. Es war das erste Mal, dass er fürchtete, infolge Explosionslärms sein Gehör zu verlieren. In den kommenden Jahren sollte er oft die Ohren zu- und den Mund offenhalten müssen, um sich wenigstens die Möglichkeit der angezielten Berufsausübung zu erhalten – wenn es überhaupt je dazu kommen würde. *** **DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!** ***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos* ***[hier](https://pareto.space/a/naddr1qqsxydty8qek2wpsvyck2wphxajrvefjvesngcfhxenrgdty89nrzvgzyzrxuqfepp2e79w9aluaz2252vyz7qdpld05pgjmeurhdgm2jv6w2qcyqqq823cpp4mhxue69uhkummn9ekx7mqprpmhxue69uhkummnw3ezuurpwfjhgmewwdcxzcm9qythwumn8ghj7mn0wd68ytnsv9ex2ar09e6x7amwqyf8wumn8ghj7mmxve3ksctfdch8qatzqythwumn8ghj7urpwfjhgmewdehhxarjxyhxxmmdszcvqk)*** *oder am Ende des Textes.* *** Schon nach kurzer Zeit änderte sich die Befehlslage wieder. Der Musikstudent wurde nun zum Infanteristen und nach Russland an die Front verbracht. Vor ihm lagen jetzt drei Kriegsjahre: Gewalt, Dreck, Gewehrkugeln, Panzerschlachten, Granatsplitter, Luftangriffe, Entbehrungen, Hunger, Kälte, sieben Verwundungen, Blut und Schmerzen, Sterbende überall, Tote, Schreiende. Verzweiflung. Sorgen. Ängste. Todesangst. Zurückweichen? Verboten! Und die stets klare Ansage dazu: Wer nicht da vorne gegen den Feind um sein Leben kämpft, dem wird es ganz sicher da hinten von den eigenen Kameraden genommen. Ein gewährter Fronturlaub 1944 versprach glückliche Momente. Zurück zu den Eltern, zurück zu den Schwestern, zurück nach Freiburg. Doch die Familie war nicht zu Hause, die Türen verschlossen. Eine Nachbarin öffnete ihr Fenster und rief dem Ratlosen zu: „Beeil‘ dich! Renn‘ zum Friedhof. Der Vater ist tot. Sie sind alle bei der Beerdigung!“ Wieder hieß es, qualvoll Abschied nehmen. Zurück an die Front. Nach einem weiteren russischen Winter brach sich unübersehbar die Erkenntnis Bahn, dass der Krieg nun seinem Ende zugehe. Doch das Bemühen im Rückzug, sich mit einem versprengten Haufen irgendwie Richtung Heimat orientieren zu können, wurde doppelt jäh unterbrochen. Fanatische Vorgesetzte befahlen die längst Geschlagenen wieder gen Osten. Kurz darauf fielen sie heranrückenden russischen Truppen in die Hände. ### Kriegsgefangenschaft: Tabakration gegen Brot Drei Jahre dem Tod entgangen, schwer verletzt und erschöpft war der 21-jährige also nun ein Kriegsgefangener. Jetzt lagen drei Jahre russischer Kriegsgefangenschaft vor ihm. Ständig war unklar, wie es weiterginge. Unmöglich jedenfalls, sich noch wie ein Pfadfinder aus den Wäldern zu ernähren. Es begannen die Jahre des Schlafens auf Brettern, die Zeit der ziellosen Zugtransporte an unbekannte Orte. Niemand sprach. Nur der Sonnenstand machte klar: Es ging nie Richtung Heimat, sondern immer weiter nach Osten. Weil der Blechbläser nicht rauchte, konnte er seine Tabakration gegen Brot tauschen. So überlebte er auch die Zeit des Hungers und der Morde in den Lagern, die Horrorbilder der nachts Erschlagenen und in die Latrinen geworfenen Toten, der sinnlosen Zwangsarbeiten und der allgegenwärtigen Wanzen. Wer versuchte zu fliehen, der wurde erschossen und sein Körper zur Abschreckung in den Fangdrähten belassen. Im Sommer stanken die dort verwesenden Leichen, wenn nicht Vögel sie rechtzeitig gefressen hatten. Als der 24-jährige schließlich sechs Jahre nach seiner Einberufung aus russischer Kriegsgefangenschaft entlassen wurde, gab es kein Zurück mehr in seine schlesische Heimat. Abgemagert reiste er der vertriebenen Mutter nach, die mit seinen Schwestern und Millionen anderen Flüchtlingen im Westen Deutschlands verteilt worden war. Kraft Ordnungsverfügung wohnte sie jetzt im sauerländischen Bad Laasphe in einem schimmligen Garagenanbau. Als ihn ein Passant auf dieser Reise morgens allein, nur mit einem Becher an der Schnur um den Hals, auf Krücken durch Berlin ziehen sah, gab er ihm schweigend sein Butterbrot. Der kleine, sanfte Junge aus dem schlesischen Freiburg hat danach noch 60 Jahre gelebt. Es dauerte zunächst sechs Jahre, bis er wieder kräftig genug war, ein Instrument zu spielen. 30-jährig saß er dann endlich in einem Orchester und begann ein normales Berufsleben. Aber sein Körper und seine Seele waren für immer aus jeder Normalität gerissen. Irgendwo in Russland war ihm die linke Hüfte so versteift worden, dass sich seine Beine im Liegen an Wade und Schienbein überkreuzten. Er musste also stets den Oberkörper vorbeugen, um überhaupt laufen zu können. Über die Jahrzehnte verzog sich so sein gesamter Knochenbau. Jeder Tag brachte neue orthopädische Probleme und Schmerzen. Ärzte, Masseure, Physiotherapeuten, Schmerzmittel und Spezialausrüstungen aller Art prägten die Tagesabläufe. Asymmetrisch standen seine Schuhe nebeneinander, die ein Spezialschuster ihm mit erhöhter Sohle und Seitenstabilisierung am Knöchel fertigte. Sessel oder Sofas waren ihm nicht nutzbar, da er nur auf einem Spezialstuhl mit halb abgesenkter Sitzfläche Ruhe fand. Auf fremden Stühlen konnte er nur deren Vorderkante nutzen. ### "In den Nächten schrie er im Schlaf" Und auch wenn er sich ohne Krankheitstage bis zuletzt durch seinen Berufsalltag kämpfte, so gab es doch viele Tage voller entsetzlicher Schmerzen, wenn sich seine verdrehte Wirbelsäule zur Migräne in den Kopf bohrte. Bei alledem hörte man ihn allerdings niemals über sein Schicksal klagen. Er ertrug den ganzen Wahnsinn mit einer unbeschreiblichen Duldsamkeit. Nur in den Nächten schrie er bisweilen im Schlaf. In einem seiner Alpträume fürchtete er, Menschen getötet zu haben. Aber auch das erzählte er jahrzehntelang einzig seiner Frau. Als sich einige Jahre vor seinem Tod der orthopädische Zustand weiter verschlechterte, konsultierte er einen Operateur, um Entlastungsmöglichkeiten zu erörtern. Der legte ihn auf eine Untersuchungsliege und empfahl, Verbesserungsversuche zu unterlassen, weil sie die Lage allenfalls verschlechtern konnten. In dem Moment, als er sich von der Liege erheben sollte, wurde deutlich, dass ihm dies nicht gelang. Die gereichte Hand, um ihn hochzuziehen, ignorierte er. Stattdessen rieb er seinen Rumpf ganz alleine eine quälend lange Minute über die Fläche, bis er endlich einen Winkel fand, um sich selbst in die Senkrechte zu bugsieren. Sich nicht auf andere verlassen, war sein Überlebenskonzept. Jahre später, als sich sein Zustand noch weiter verschlechtert hatte, lächelte er über seine Behinderung: „Ich hätte schon vor 60 Jahren tot auf einem Acker in Russland liegen können.“ Alles gehe irgendwann vorbei, tröstete er sich. Das war das andere Überlebenskonzept: liebevoll, friedfertig und sanft anderen gegenüber, unerbittlich mit sich selbst. Sechs Monate vor seinem Tod saß er morgens regungslos auf seinem Spezialstuhl. Eine Altenpflegerin fand ihn und schlug Alarm. Mit allen Kunstgriffen der medizinischen Technik wurde er noch einmal in das Leben zurückkatapultiert. Aber seine Kräfte waren erschöpft. Es schob sich das Grauen der Vergangenheit zwischen ihn und die Welt. Bettlägerig kreiste er um sich selbst, erkannte niemanden und starrte mit weit offenen Augen an die Decke. „Die Russen schmeißen wieder Brandbomben!“, war einer seiner letzten Sätze. Der kleine Junge aus Schlesien ist nicht zu weich geraten. Er hat sein Leid mit unbeugsamer Duldsamkeit ertragen. Er trug es wohl als Strafe für das Leid, das er anderen anzutun genötigt worden war. An seinem Geburtstag blühen immer die Magnolien. In diesem Jahr zum hundertsten Mal. *Dieser Text wurde am 23.3.2024 erstveröffentlicht auf* *[„eigentümlich frei“.](https://ef-magazin.de/2024/03/23/21072-make-love-not-law-kriegstuechtig)* *** *Carlos A. Gebauer studierte Philosophie, Neuere Geschichte, Sprach-, Rechts- und Musikwissenschaften in Düsseldorf, Bayreuth und Bonn. Sein juristisches Referendariat absolvierte er in Düsseldorf, u.a. mit Wahlstationen bei der Landesrundfunkanstalt NRW, bei der Spezialkammer für Kassenarztrecht des Sozialgerichtes Düsseldorf und bei dem Gnadenbeauftragten der Staatsanwaltschaft Düsseldorf.* *Er war unter anderem als Rechtsanwalt und Notarvertreter bis er im November 2003 vom nordrhein-westfälischen Justizministerium zum Richter am Anwaltsgericht für den Bezirk der Rechtsanwaltskammer Düsseldorf ernannt wurde. Seit April 2012 arbeitet er in der Düsseldorfer Rechtsanwaltskanzlei Lindenau, Prior & Partner. Im Juni 2015 wählte ihn die Friedrich-August-von-Hayek-Gesellschaft zu ihrem Stellvertretenden Vorsitzenden. Seit Dezember 2015 ist er Richter im Zweiten Senat des Anwaltsgerichtshofes NRW.* *1995 hatte er parallel zu seiner anwaltlichen Tätigkeit mit dem Verfassen gesellschaftspolitischer und juristischer Texte begonnen. Diese erschienen seither unter anderem in der Neuen Juristischen Wochenschrift (NJW), der Zeitschrift für Rechtspolitik (ZRP) in der [Frankfurter Allgemeinen Zeitung](http://www.faz.de/), der [Freien Presse Chemnitz](http://www.freiepresse.de/), dem „Schweizer Monat“ oder dem Magazin für politische Kultur CICERO. Seit dem Jahr 2005 ist Gebauer ständiger Kolumnist und Autor des Magazins „eigentümlich frei“.* *Gebauer glaubt als puristischer Liberaler unverbrüchlich an die sittliche Verpflichtung eines jeden einzelnen, sein Leben für sich selbst und für seine Mitmenschen verantwortlich zu gestalten; jede Fremdbestimmung durch Gesetze, staatliche Verwaltung, politischen Einfluss oder sonstige Gewalteinwirkung hat sich demnach auf ein ethisch vertretbares Minimum zu beschränken. Die Vorstellung eines europäischen Bundesstaates mit zentral detailsteuernder, supranationaler Staatsgewalt hält er für absurd und verfassungswidrig.* \ **Aktuelle Bücher:** Hayeks Warnung vor der Knechtschaft (2024) – [hier im Handel](https://www.buchkomplizen.de/hayeks-warnung-vor-der-knechtschaft.html?listtype=search\&searchparam=Carlos%2520A%2520gebauer) Das Prinzip Verantwortungslosigkeit (2023) – [hier im Handel](https://www.buchkomplizen.de/das-prinzip-verantwortungslosigkeit.html?listtype=search\&searchparam=Carlos%2520A%2520gebauer) *** **LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!** ***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.* Schon jetzt können Sie uns unterstützen: * Für **50 CHF/EURO** bekommen Sie ein Jahresabo der Friedenstaube. * Für **120 CHF/EURO** bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube. * Für **500 CHF/EURO** werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube. * Ab **1000 CHF** werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie). **Für Einzahlungen in CHF (Betreff: Friedenstaube):** 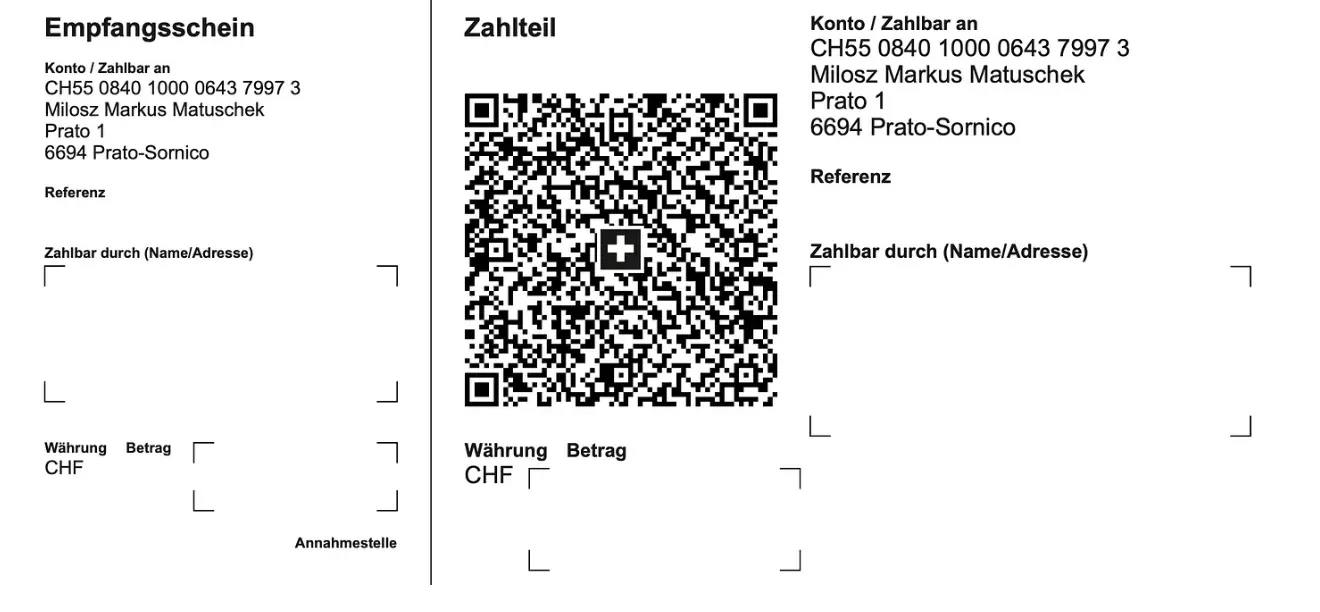 **Für Einzahlungen in Euro:** Milosz Matuschek IBAN DE 53710520500000814137 BYLADEM1TST Sparkasse Traunstein-Trostberg **Betreff: Friedenstaube** Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: <milosz@pareto.space> *** **Sie sind noch nicht auf** [Nostr](https://nostr.com/) **and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil!** Erstellen Sie sich einen Account auf [Start.](https://start.njump.me/) Weitere Onboarding-Leitfäden gibt es im [Pareto-Wiki.](https://wiki.pareto.space/de/home) @ 2e8970de:63345c7a
2025-03-31 19:08:11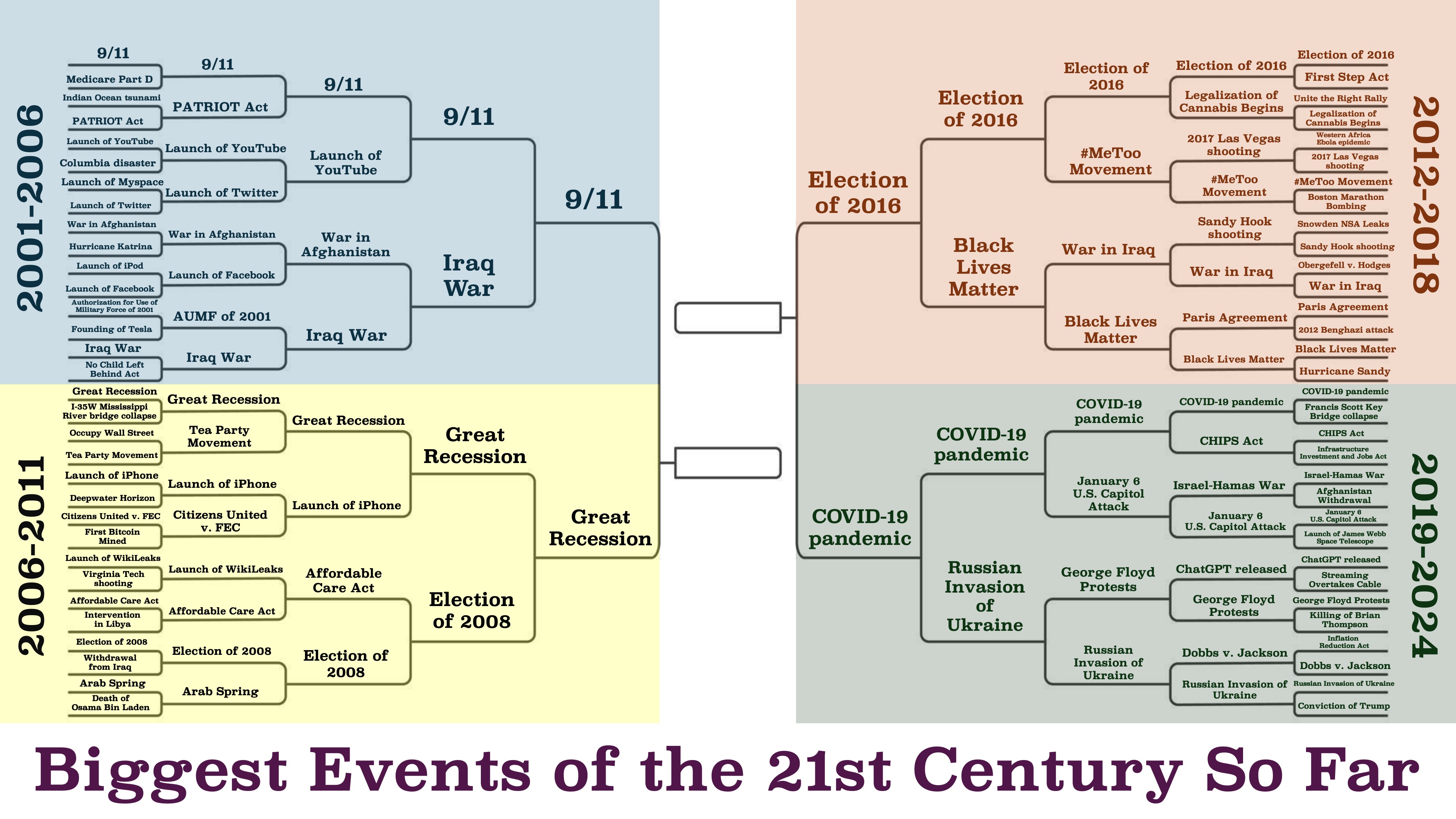 https://x.com/beatmastermatt/status/1906329250115858750 originally posted at https://stacker.news/items/930491
@ 2e8970de:63345c7a
2025-03-31 19:08:11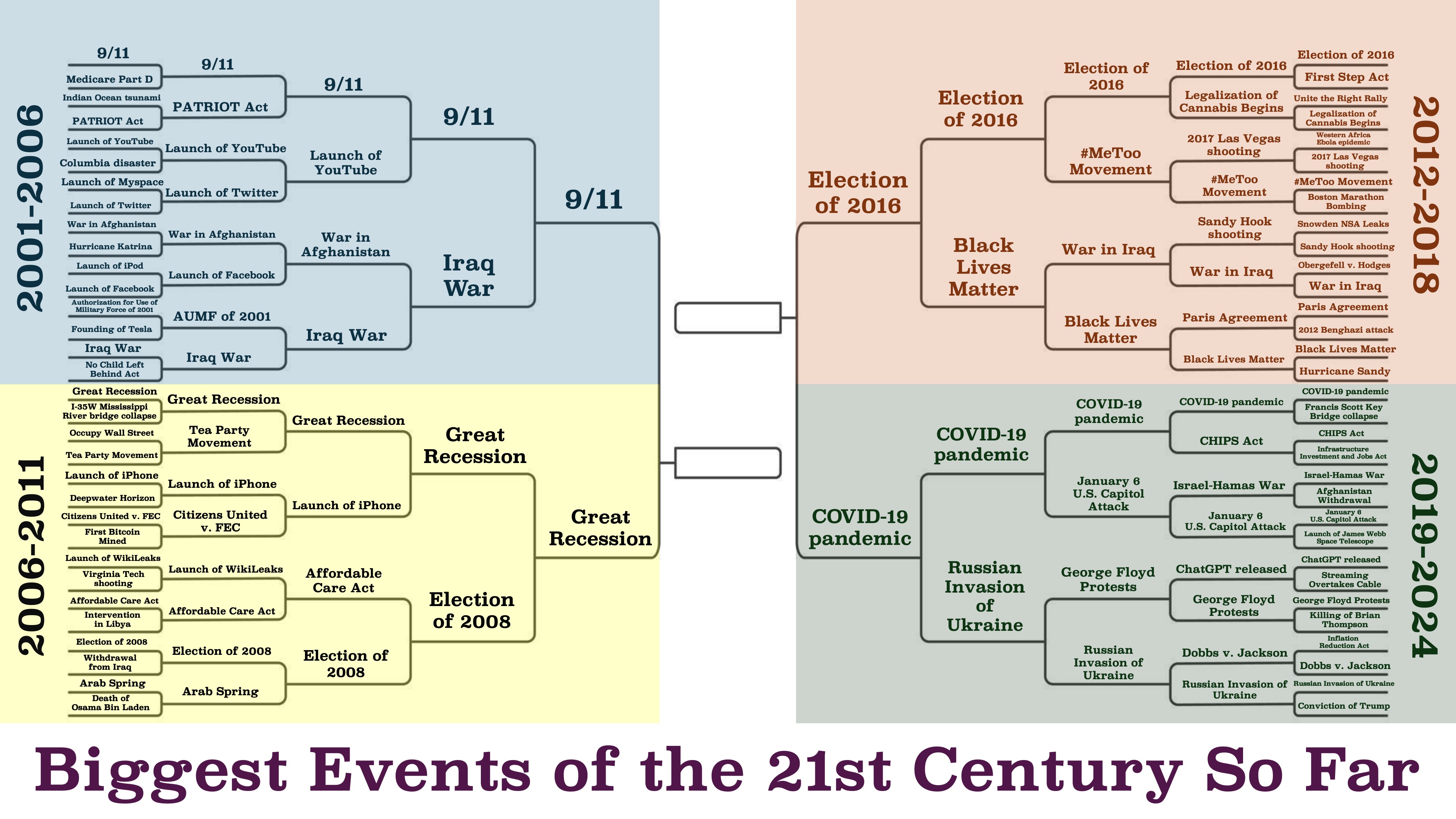 https://x.com/beatmastermatt/status/1906329250115858750 originally posted at https://stacker.news/items/930491 @ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get [this line](https://www.youtube.com/shorts/kqsomjpz7ok): “Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.” Yesterday, I came across a comment on the song [Devil Went Down to Georgia](https://youtu.be/ut8UqFlWdDc) that had a very similar feel to it:  America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans. That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form. For most countries, saying “our nation is the greatest” *is*, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people *should* be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence. But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America. That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is *freedom*. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit. American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are *definitionally* better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.) In *Devil Went Down to Georgia*, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.” *Libertas magnitudo est*
@ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get [this line](https://www.youtube.com/shorts/kqsomjpz7ok): “Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.” Yesterday, I came across a comment on the song [Devil Went Down to Georgia](https://youtu.be/ut8UqFlWdDc) that had a very similar feel to it:  America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans. That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form. For most countries, saying “our nation is the greatest” *is*, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people *should* be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence. But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America. That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is *freedom*. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit. American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are *definitionally* better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.) In *Devil Went Down to Georgia*, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.” *Libertas magnitudo est* @ bcbb3e40:a494e501
2025-03-31 16:00:24|[](https://amzn.to/4jaGBZ4)| |:-:| |[WAJDA, Andrzej; _Cenizas y diamantes_, 1958](https://amzn.to/4jaGBZ4)| Presentamos una nueva reseña cinematográfica, y en esta ocasión hemos elegido «Cenizas y diamantes», una película polaca del célebre y prolífico director **Andrzej Wajda** (1926-2016), estrenada en el año 1958. Se trata de uno de los grandes clásicos del cine polaco. El filme refleja una etapa dramática desde la perspectiva histórica para la nación polaca, como es el final de la Segunda Guerra Mundial, a raíz de la capitulación alemana del 8 de mayo de 1945. El contexto en el que se desarrolla se ambienta en la celebración del final de la guerra con el aplastante triunfo de la URSS, con las tropas soviéticas ocupando toda la Europa oriental, y en particular Polonia, que vive un momento de oscuridad e incertidumbre. El protagonista, **Maciek Chełmicki** (interpretado magistralmente por **Zbigniew Cybulski** (1927-1967), apodado el «James Dean polaco»), es un joven nacionalista polaco, de orientación anticomunista, que se ve implicado en un complot urdido para asesinar a un líder comunista local. Maciek opera desde la clandestinidad, bajo el grupo **Armia Krajowa (AK)**, el Ejército Nacional polaco, una organización de resistencia, primero contra los alemanes y, posteriormente, contra los soviéticos. Durante el metraje, se plantea una dicotomía permanente entre la libertad entendida como la defensa de la soberanía de Polonia, desde posturas nacionalistas, y quienes consideran la ocupación soviética como algo positivo. Estas circunstancias atrapan al protagonista, que se ve envuelto en una espiral de violencia y traición. Maciek Chełmicki, nuestro protagonista, cuenta con todas [las características del héroe trágico](https://hiperbolajanus.com/posts/caballero-muerte-diablo-jean-cau/), pues tiene en sus manos una serie de acciones que comprometen el futuro de un pueblo, que consiste en cumplir la misión que le ha sido encomendada, pero en su camino se cruza una joven, Krystyna, una joven camarera de un hotel de la que se enamora en ese mismo día. Este último hecho sirve de punto de partida para todas las dudas, dilemas y dicotomías a las que hacemos referencia. Hay un dilema moral evidente en un mundo en ruinas, [devastado por la guerra, la muerte y el nihilismo](https://hiperbolajanus.com/posts/en-el-mar-de-la-nada-curzio-nitoglia/). En este sentido Wajda nos muestra un lenguaje cinematográfico muy evidente, a través de una técnica expresionista muy depurada, con el uso del blanco y negro, los contrastes generados por las sombras y la atmósfera opresiva que transmite angustia, desesperación y vulnerabilidad de los protagonistas. Además también destilan una fuerte carga emocional, donde no están exentos elementos poéticos y un poderoso lirismo. || |:-:| |Maciek Chełmicki, el protagonista.| Hay elementos simbólicos que no podemos obviar, y que contribuyen a consolidar el análisis que venimos haciendo, como, por ejemplo, la estética del protagonista, con unas gafas oscuras, que actúan como una suerte de barrera frente al mundo que le rodea, como parte del anonimato tras el cual el joven Maciek vive de forma introspectiva su propio drama particular y el de toda una nación. |[](https://www.hiperbolajanus.com/libros/mar-nada-curzio-nitoglia/)| |:-:| |[NITOGLIA, Curzio; _En el mar de la nada: Metafísica y nihilismo a prueba en la posmodernidad_; Hipérbola Janus, 2023](https://www.hiperbolajanus.com/libros/mar-nada-curzio-nitoglia/)| Hay una escena especialmente poderosa, y casi mítica, en la que los dos jóvenes protagonistas, Maciek y Krystina, se encuentran entre las ruinas de una Iglesia, en la que se destaca en primer plano, ocupando buena parte de la pantalla, la imagen de un Cristo invertido sobre un crucifijo, donde también se encuentran dos cuerpos colgados hacia abajo en una estampa que refleja la devastación moral y espiritual de toda una época. De hecho, [la imagen del crucifijo invertido refleja el máximo punto de subversión y profanación de lo sagrado](https://hiperbolajanus.com/posts/la-cruz-frente-la-modernidad/), y que en el caso concreto de la película viene a representar la destrucción del orden moral y de valores cristianos que la propia guerra ha provocado. Polonia es una nación profundamente católica, convertida al Cristianismo en el 966 a raíz de la conversión del príncipe **Miecislao I**, contribuyendo de manera decisiva a la formación de la identidad nacional polaca. El catolicismo siempre ha sido un medio de cohesión y defensa frente a las influencias extranjeras y la ocupación de terceros países, una constante en la historia del país, como el que ilustra la propia película con la URSS. En este sentido, la imagen de una Iglesia en ruinas, el lugar donde se encuentra representado el principio de lo sagrado e inviolable, [supone una forma de perversión de todo principio de redención y salvación frente a la tragedia](https://hiperbolajanus.com/posts/mas-nos-vale-rezar/), y al mismo tiempo viene a significar que la Tradición ha sido abandonada y pervertida. En la misma línea, el protagonista, Maciek, se encuentra atrapado en una espiral de violencia a través de sus actos terroristas perpetrados contra la autoridad soviética que ocupa su país. Los dos cuerpos anónimos que cuelgan boca abajo, de forma grotesca, también participan de este caos y desequilibrio de un orden dislocado, son parte de la deshumanización y el nihilismo que todo lo impregna. || |:-:| |Maciek y Krystina en una iglesia en ruinas| Como ya hemos mencionado, la película se encuentra plagada de paradojas y dicotomías, en las que nuestro protagonista, [el joven rebelde e inconformista](https://hiperbolajanus.com/posts/juventud-contestacion/), debe elegir permanentemente, en unas decisiones que resultan trascendentales para su futuro y el de la propia nación. La figura femenina que irrumpe en su vida, y que representa un principio disruptivo que provoca una fractura interior y una crisis, le suscita una toma de conciencia de su propia situación y le fuerza a tomar un camino entre la «felicidad», del «amor», la «esperanza» y la «vida», que le permita superar la deriva nihilista y autodestructiva de la lucha clandestina, la cual le aboca a un destino trágico (que no vamos a desentrañar para no hacer spoiler). En relación al propio título de la película, «Cenizas y diamantes», basada en el poema del poeta y dramaturgo polaco **Cyprian Norwid** (1821-1883) y en la novela del autor, también polaco, **Jerzy Andrzejewski** (1909-1983), nos destaca la dualidad de los dos elementos que lo componen, y que definen el contraste entre el mundo sombrío y oscuro (Cenizas) y la esperanza y la luz que representa susodicha figura femenina (diamantes). La segunda alternativa parece un imposible, una quimera irrealizable que se pliega ante un Destino implacable, irreversible y cruel. En consecuencia, y a la luz de los elementos expuestos, podemos decir que se nos presentan dilemas propios de la filosofía existencialista, que conoce su punto álgido en esos años, con autores como **Jean Paul Sartre** (1905-1980), **Albert Camus** (1913-1960), **Karl Jaspers** (1883-1969) o [**Martin Heidegger**](https://amzn.to/4cmjvwE) (1889-1976) entre otros. Respecto a éste último, a Heidegger, podemos encontrar algunas claves interesantes a través de su filosofía en relación al protagonista, a Maciek, especialmente a través de la idea del *Dasein*, a la idea de haber sido arrojado al mundo (*Geworfenheit*), y la manera tan extrema y visceral en la que vive susodicha condición. Todos aquellos elementos que dan sentido a la vida colectiva [se encuentran decaídos o destruidos en su esencia más íntima, la Patria, la religión o la propia idea de Comunidad orgánica](https://hiperbolajanus.com/posts/textos-tradicion-tiempos-oscurecimiento-hj/). De modo que el protagonista se ha visto «arrojado» frente a una situación o destino indeseado, en unas coyunturas totalmente desfavorables en las que no queda otra elección. Sus decisiones están permanentemente condicionadas por la circunstancia descrita y, por tanto, vive en un mundo donde no controla nada, en lugar de ser sujeto es un mero objeto transportado por esas circunstancias ajenas a su voluntad. Sin embargo, y en coherencia con el *Dasein* heideggeriano, vemos como Maciek, a raíz de conocer a Krystyna, comienza a experimentar una catarsis interior, que muestra por momentos el deseo de superar ese «ser arrojado al mundo contra tu voluntad», trascendiendo esa condición absurda e irracional de unas decisiones enajenadas de su voluntad para dotar de una significación y un sentido la propia existencia. || |:-:| |Andrzej Wajda, el director de la película.| Otro elemento característico de la filosofía heideggeriana lo podemos encontrar en la «angustia» (*angst*) a través de la ausencia de un sentido y fundamento último que justifique la existencia del protagonista. Es una angustia en a que el *Dasein* se enfrenta a la «nada», a ese vacío existencial que hace inútil toda la lucha que Maciek lleva a cabo en la clandestinidad, con asesinatos y actos de terrorismo que pretenden salvaguardar algo que ya no existe, y que simboliza muy bien la Iglesia en ruinas con sus símbolos religiosos invertidos de la que hablábamos con anterioridad. Recuerda un poco a esa dicotomía que se plantea entre ser conservador o reaccionario frente a una realidad como la del propio presente, en la que los valores tradicionales han sido totalmente destruidos, y más que conservar se impone la reacción para volver a construir de la nada. |[](https://www.hiperbolajanus.com/libros/textos-tradicion-tiempos-oscurecimiento-hiperbola-janus/)| |:-:| |[Hipérbola Janus; _Textos para la Tradición en tiempos del oscurecimiento: Artículos publicados entre 2014 y 2019 en hiperbolajanus.com_; Hipérbola Janus, 2019](https://www.hiperbolajanus.com/libros/textos-tradicion-tiempos-oscurecimiento-hiperbola-janus/)| Todas las dudas que asaltan al protagonista se ven incrementadas en el momento decisivo, cuando se dispone a dar muerte al líder comunista. Se produce una tensión interna en Maciek, que se encuentra ligado a la joven que ha conocido ese día, y en ella es donde encuentra ese leve destello de humanidad. Esa circunstancia le hace replantearse por un instante el cumplimiento de su misión, pero es un dilema que no tiene salida, y por ello le asalta nuevamente la angustia frente a esa «nada», ese mundo vacío e incomprensible que trasciende el marco de sus propias elecciones. Uno de los conceptos centrales de Heidegger en [*Ser y tiempo*](https://amzn.to/4l7uMoi) es el *Sein-zum-Tode* (*ser-para-la-muerte*), la idea de que la muerte es la posibilidad más propia y definitiva del *Dasein*, y que enfrentarla auténticamente permite vivir de manera más plena. Y es que el protagonista se encuentra permanentemente sobre esa frontera entre la vida y la muerte, que afronta con todas sus consecuencias, conscientemente, y la acepta. Esta actitud podría leerse como una forma de *Dasein* inauténtico, una huida del *ser-para-la-muerte* mediante la distracción (*das Man*, el «se» impersonal). Sin embargo, su decisión de cumplir la misión sugiere un enfrentamiento final con esa posibilidad. Otro aspecto que podemos conectar con el pensamiento heideggeriano es la autenticidad o inautenticidad de la vida del protagonista. En relación a la inautenticidad vemos como al principio sigue las órdenes de sus superiores en la organización sin cuestionarlas, lo cual implica un comportamiento inequívocamente alienante. Respecto a aquello que resulta auténtico de su existencia son sus relaciones con Krystyna, que supone imponer su propia voluntad y decisión, mostrando un *Dasein* que asume su libertad. || |:-:| |Escena de la película.| Otros aspectos más generales de la filosofía existencialista redundan sobre estos mismos aspectos, con la elección entre la libertad absoluta y la condena inevitable. La idea del hombre condenado a actuar, a una elección continua, aún cuando el hombre no es dueño de su destino, o las consecuencias de tales acciones son absurdas, irracionales e incomprensibles. El propio absurdo de la existencia frente al vacío y la ausencia de principios sólidos en los que cimentar la vida, no solo en sus aspectos cotidianos más básicos, sino en aquellos más profundos de la existencia. La soledad y la propia fatalidad frente a un Destino que, como ya hemos apuntado anteriormente, parece imponerse de manera irrevocable, y podríamos decir que brutalmente, al individuo aislado, incapaz de asirse en una guía, en unos valores que le permitan remontar la situación. En términos generales «Cenizas y diamantes», además de ser una película de gran calidad en sus aspectos técnicos, en su fotografía, en la configuración de sus escenas y en el propio desarrollo argumental, bajo un guión espléndidamente ejecutado a lo largo de sus 98 minutos de duración, también nos invita a una reflexión profunda sobre la condición humana y la propia Modernidad. Y es algo que vemos en nuestros días, con las consecuencias de un pensamiento débil, con la promoción del individualismo, el hedonismo y lo efímero. La ausencia de estructuras sólidas, [la subversión de toda forma de autoridad y jerarquía tradicionales](https://hiperbolajanus.com/posts/metapolitica-tradicion-modernidad-antologia-julius-evola/). Paradójicamente, el mundo actual tiende a formas de poder y autoridad mucho más invasivas y coercitivas, tanto a nivel individual como colectivo, pero en la misma línea abstracta e impersonal que nos describe la película, abocándonos a la alienación y la inautenticidad de nuestras propias vidas. Y como Maciek, también nosotros, vivimos en un mundo dominado por la incertidumbre y la desesperanza, en el que el globalismo y sus perversas ideologías deshumanizantes actúan por doquier. || |:-:| |Carátula original de la película en polaco.| --- **Artículo original**: Hipérbola Janus, [_Reseña de «Cenizas y Diamantes» (Andrzej Wajda, 1958)_](https://www.hiperbolajanus.com/posts/resena-cenizas-diamantes/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/resena-cenizas-diamantes/), 31/Mar/2025
@ bcbb3e40:a494e501
2025-03-31 16:00:24|[](https://amzn.to/4jaGBZ4)| |:-:| |[WAJDA, Andrzej; _Cenizas y diamantes_, 1958](https://amzn.to/4jaGBZ4)| Presentamos una nueva reseña cinematográfica, y en esta ocasión hemos elegido «Cenizas y diamantes», una película polaca del célebre y prolífico director **Andrzej Wajda** (1926-2016), estrenada en el año 1958. Se trata de uno de los grandes clásicos del cine polaco. El filme refleja una etapa dramática desde la perspectiva histórica para la nación polaca, como es el final de la Segunda Guerra Mundial, a raíz de la capitulación alemana del 8 de mayo de 1945. El contexto en el que se desarrolla se ambienta en la celebración del final de la guerra con el aplastante triunfo de la URSS, con las tropas soviéticas ocupando toda la Europa oriental, y en particular Polonia, que vive un momento de oscuridad e incertidumbre. El protagonista, **Maciek Chełmicki** (interpretado magistralmente por **Zbigniew Cybulski** (1927-1967), apodado el «James Dean polaco»), es un joven nacionalista polaco, de orientación anticomunista, que se ve implicado en un complot urdido para asesinar a un líder comunista local. Maciek opera desde la clandestinidad, bajo el grupo **Armia Krajowa (AK)**, el Ejército Nacional polaco, una organización de resistencia, primero contra los alemanes y, posteriormente, contra los soviéticos. Durante el metraje, se plantea una dicotomía permanente entre la libertad entendida como la defensa de la soberanía de Polonia, desde posturas nacionalistas, y quienes consideran la ocupación soviética como algo positivo. Estas circunstancias atrapan al protagonista, que se ve envuelto en una espiral de violencia y traición. Maciek Chełmicki, nuestro protagonista, cuenta con todas [las características del héroe trágico](https://hiperbolajanus.com/posts/caballero-muerte-diablo-jean-cau/), pues tiene en sus manos una serie de acciones que comprometen el futuro de un pueblo, que consiste en cumplir la misión que le ha sido encomendada, pero en su camino se cruza una joven, Krystyna, una joven camarera de un hotel de la que se enamora en ese mismo día. Este último hecho sirve de punto de partida para todas las dudas, dilemas y dicotomías a las que hacemos referencia. Hay un dilema moral evidente en un mundo en ruinas, [devastado por la guerra, la muerte y el nihilismo](https://hiperbolajanus.com/posts/en-el-mar-de-la-nada-curzio-nitoglia/). En este sentido Wajda nos muestra un lenguaje cinematográfico muy evidente, a través de una técnica expresionista muy depurada, con el uso del blanco y negro, los contrastes generados por las sombras y la atmósfera opresiva que transmite angustia, desesperación y vulnerabilidad de los protagonistas. Además también destilan una fuerte carga emocional, donde no están exentos elementos poéticos y un poderoso lirismo. || |:-:| |Maciek Chełmicki, el protagonista.| Hay elementos simbólicos que no podemos obviar, y que contribuyen a consolidar el análisis que venimos haciendo, como, por ejemplo, la estética del protagonista, con unas gafas oscuras, que actúan como una suerte de barrera frente al mundo que le rodea, como parte del anonimato tras el cual el joven Maciek vive de forma introspectiva su propio drama particular y el de toda una nación. |[](https://www.hiperbolajanus.com/libros/mar-nada-curzio-nitoglia/)| |:-:| |[NITOGLIA, Curzio; _En el mar de la nada: Metafísica y nihilismo a prueba en la posmodernidad_; Hipérbola Janus, 2023](https://www.hiperbolajanus.com/libros/mar-nada-curzio-nitoglia/)| Hay una escena especialmente poderosa, y casi mítica, en la que los dos jóvenes protagonistas, Maciek y Krystina, se encuentran entre las ruinas de una Iglesia, en la que se destaca en primer plano, ocupando buena parte de la pantalla, la imagen de un Cristo invertido sobre un crucifijo, donde también se encuentran dos cuerpos colgados hacia abajo en una estampa que refleja la devastación moral y espiritual de toda una época. De hecho, [la imagen del crucifijo invertido refleja el máximo punto de subversión y profanación de lo sagrado](https://hiperbolajanus.com/posts/la-cruz-frente-la-modernidad/), y que en el caso concreto de la película viene a representar la destrucción del orden moral y de valores cristianos que la propia guerra ha provocado. Polonia es una nación profundamente católica, convertida al Cristianismo en el 966 a raíz de la conversión del príncipe **Miecislao I**, contribuyendo de manera decisiva a la formación de la identidad nacional polaca. El catolicismo siempre ha sido un medio de cohesión y defensa frente a las influencias extranjeras y la ocupación de terceros países, una constante en la historia del país, como el que ilustra la propia película con la URSS. En este sentido, la imagen de una Iglesia en ruinas, el lugar donde se encuentra representado el principio de lo sagrado e inviolable, [supone una forma de perversión de todo principio de redención y salvación frente a la tragedia](https://hiperbolajanus.com/posts/mas-nos-vale-rezar/), y al mismo tiempo viene a significar que la Tradición ha sido abandonada y pervertida. En la misma línea, el protagonista, Maciek, se encuentra atrapado en una espiral de violencia a través de sus actos terroristas perpetrados contra la autoridad soviética que ocupa su país. Los dos cuerpos anónimos que cuelgan boca abajo, de forma grotesca, también participan de este caos y desequilibrio de un orden dislocado, son parte de la deshumanización y el nihilismo que todo lo impregna. || |:-:| |Maciek y Krystina en una iglesia en ruinas| Como ya hemos mencionado, la película se encuentra plagada de paradojas y dicotomías, en las que nuestro protagonista, [el joven rebelde e inconformista](https://hiperbolajanus.com/posts/juventud-contestacion/), debe elegir permanentemente, en unas decisiones que resultan trascendentales para su futuro y el de la propia nación. La figura femenina que irrumpe en su vida, y que representa un principio disruptivo que provoca una fractura interior y una crisis, le suscita una toma de conciencia de su propia situación y le fuerza a tomar un camino entre la «felicidad», del «amor», la «esperanza» y la «vida», que le permita superar la deriva nihilista y autodestructiva de la lucha clandestina, la cual le aboca a un destino trágico (que no vamos a desentrañar para no hacer spoiler). En relación al propio título de la película, «Cenizas y diamantes», basada en el poema del poeta y dramaturgo polaco **Cyprian Norwid** (1821-1883) y en la novela del autor, también polaco, **Jerzy Andrzejewski** (1909-1983), nos destaca la dualidad de los dos elementos que lo componen, y que definen el contraste entre el mundo sombrío y oscuro (Cenizas) y la esperanza y la luz que representa susodicha figura femenina (diamantes). La segunda alternativa parece un imposible, una quimera irrealizable que se pliega ante un Destino implacable, irreversible y cruel. En consecuencia, y a la luz de los elementos expuestos, podemos decir que se nos presentan dilemas propios de la filosofía existencialista, que conoce su punto álgido en esos años, con autores como **Jean Paul Sartre** (1905-1980), **Albert Camus** (1913-1960), **Karl Jaspers** (1883-1969) o [**Martin Heidegger**](https://amzn.to/4cmjvwE) (1889-1976) entre otros. Respecto a éste último, a Heidegger, podemos encontrar algunas claves interesantes a través de su filosofía en relación al protagonista, a Maciek, especialmente a través de la idea del *Dasein*, a la idea de haber sido arrojado al mundo (*Geworfenheit*), y la manera tan extrema y visceral en la que vive susodicha condición. Todos aquellos elementos que dan sentido a la vida colectiva [se encuentran decaídos o destruidos en su esencia más íntima, la Patria, la religión o la propia idea de Comunidad orgánica](https://hiperbolajanus.com/posts/textos-tradicion-tiempos-oscurecimiento-hj/). De modo que el protagonista se ha visto «arrojado» frente a una situación o destino indeseado, en unas coyunturas totalmente desfavorables en las que no queda otra elección. Sus decisiones están permanentemente condicionadas por la circunstancia descrita y, por tanto, vive en un mundo donde no controla nada, en lugar de ser sujeto es un mero objeto transportado por esas circunstancias ajenas a su voluntad. Sin embargo, y en coherencia con el *Dasein* heideggeriano, vemos como Maciek, a raíz de conocer a Krystyna, comienza a experimentar una catarsis interior, que muestra por momentos el deseo de superar ese «ser arrojado al mundo contra tu voluntad», trascendiendo esa condición absurda e irracional de unas decisiones enajenadas de su voluntad para dotar de una significación y un sentido la propia existencia. || |:-:| |Andrzej Wajda, el director de la película.| Otro elemento característico de la filosofía heideggeriana lo podemos encontrar en la «angustia» (*angst*) a través de la ausencia de un sentido y fundamento último que justifique la existencia del protagonista. Es una angustia en a que el *Dasein* se enfrenta a la «nada», a ese vacío existencial que hace inútil toda la lucha que Maciek lleva a cabo en la clandestinidad, con asesinatos y actos de terrorismo que pretenden salvaguardar algo que ya no existe, y que simboliza muy bien la Iglesia en ruinas con sus símbolos religiosos invertidos de la que hablábamos con anterioridad. Recuerda un poco a esa dicotomía que se plantea entre ser conservador o reaccionario frente a una realidad como la del propio presente, en la que los valores tradicionales han sido totalmente destruidos, y más que conservar se impone la reacción para volver a construir de la nada. |[](https://www.hiperbolajanus.com/libros/textos-tradicion-tiempos-oscurecimiento-hiperbola-janus/)| |:-:| |[Hipérbola Janus; _Textos para la Tradición en tiempos del oscurecimiento: Artículos publicados entre 2014 y 2019 en hiperbolajanus.com_; Hipérbola Janus, 2019](https://www.hiperbolajanus.com/libros/textos-tradicion-tiempos-oscurecimiento-hiperbola-janus/)| Todas las dudas que asaltan al protagonista se ven incrementadas en el momento decisivo, cuando se dispone a dar muerte al líder comunista. Se produce una tensión interna en Maciek, que se encuentra ligado a la joven que ha conocido ese día, y en ella es donde encuentra ese leve destello de humanidad. Esa circunstancia le hace replantearse por un instante el cumplimiento de su misión, pero es un dilema que no tiene salida, y por ello le asalta nuevamente la angustia frente a esa «nada», ese mundo vacío e incomprensible que trasciende el marco de sus propias elecciones. Uno de los conceptos centrales de Heidegger en [*Ser y tiempo*](https://amzn.to/4l7uMoi) es el *Sein-zum-Tode* (*ser-para-la-muerte*), la idea de que la muerte es la posibilidad más propia y definitiva del *Dasein*, y que enfrentarla auténticamente permite vivir de manera más plena. Y es que el protagonista se encuentra permanentemente sobre esa frontera entre la vida y la muerte, que afronta con todas sus consecuencias, conscientemente, y la acepta. Esta actitud podría leerse como una forma de *Dasein* inauténtico, una huida del *ser-para-la-muerte* mediante la distracción (*das Man*, el «se» impersonal). Sin embargo, su decisión de cumplir la misión sugiere un enfrentamiento final con esa posibilidad. Otro aspecto que podemos conectar con el pensamiento heideggeriano es la autenticidad o inautenticidad de la vida del protagonista. En relación a la inautenticidad vemos como al principio sigue las órdenes de sus superiores en la organización sin cuestionarlas, lo cual implica un comportamiento inequívocamente alienante. Respecto a aquello que resulta auténtico de su existencia son sus relaciones con Krystyna, que supone imponer su propia voluntad y decisión, mostrando un *Dasein* que asume su libertad. || |:-:| |Escena de la película.| Otros aspectos más generales de la filosofía existencialista redundan sobre estos mismos aspectos, con la elección entre la libertad absoluta y la condena inevitable. La idea del hombre condenado a actuar, a una elección continua, aún cuando el hombre no es dueño de su destino, o las consecuencias de tales acciones son absurdas, irracionales e incomprensibles. El propio absurdo de la existencia frente al vacío y la ausencia de principios sólidos en los que cimentar la vida, no solo en sus aspectos cotidianos más básicos, sino en aquellos más profundos de la existencia. La soledad y la propia fatalidad frente a un Destino que, como ya hemos apuntado anteriormente, parece imponerse de manera irrevocable, y podríamos decir que brutalmente, al individuo aislado, incapaz de asirse en una guía, en unos valores que le permitan remontar la situación. En términos generales «Cenizas y diamantes», además de ser una película de gran calidad en sus aspectos técnicos, en su fotografía, en la configuración de sus escenas y en el propio desarrollo argumental, bajo un guión espléndidamente ejecutado a lo largo de sus 98 minutos de duración, también nos invita a una reflexión profunda sobre la condición humana y la propia Modernidad. Y es algo que vemos en nuestros días, con las consecuencias de un pensamiento débil, con la promoción del individualismo, el hedonismo y lo efímero. La ausencia de estructuras sólidas, [la subversión de toda forma de autoridad y jerarquía tradicionales](https://hiperbolajanus.com/posts/metapolitica-tradicion-modernidad-antologia-julius-evola/). Paradójicamente, el mundo actual tiende a formas de poder y autoridad mucho más invasivas y coercitivas, tanto a nivel individual como colectivo, pero en la misma línea abstracta e impersonal que nos describe la película, abocándonos a la alienación y la inautenticidad de nuestras propias vidas. Y como Maciek, también nosotros, vivimos en un mundo dominado por la incertidumbre y la desesperanza, en el que el globalismo y sus perversas ideologías deshumanizantes actúan por doquier. || |:-:| |Carátula original de la película en polaco.| --- **Artículo original**: Hipérbola Janus, [_Reseña de «Cenizas y Diamantes» (Andrzej Wajda, 1958)_](https://www.hiperbolajanus.com/posts/resena-cenizas-diamantes/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/resena-cenizas-diamantes/), 31/Mar/2025 @ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy [article on the pros of a strategic Bitcoin reserve](https://geek.npub.pro/post/dxqkgnjplttkvetprg8ox/), I wanted to take some time to chime in on the much more fun topic of digital engagement. Let's begin by defining a couple of things: **Nostr** is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example. **Zap** is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what [Lightning](https://lightning.network/) or [Cashu](https://cashu.space/) are. If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article. In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed. What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.  Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines. That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems. Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.  I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives. Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms? Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life? If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later. 
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy [article on the pros of a strategic Bitcoin reserve](https://geek.npub.pro/post/dxqkgnjplttkvetprg8ox/), I wanted to take some time to chime in on the much more fun topic of digital engagement. Let's begin by defining a couple of things: **Nostr** is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example. **Zap** is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what [Lightning](https://lightning.network/) or [Cashu](https://cashu.space/) are. If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article. In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed. What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.  Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines. That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems. Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.  I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives. Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms? Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life? If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.  @ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a [friendly discussion](https://x.com/snoyberg/status/1887007888117252142) on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it! The US healthcare system is essentially the worst of both worlds: * Unlike full single payer, individuals incur high costs * Unlike a true free market, regulation causes increases in costs and decreases competition among insurers I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do: * Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice. * Reduce regulations significantly. * In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways: 1. Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices. 2. Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.) Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation. And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers. And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply." https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a [friendly discussion](https://x.com/snoyberg/status/1887007888117252142) on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it! The US healthcare system is essentially the worst of both worlds: * Unlike full single payer, individuals incur high costs * Unlike a true free market, regulation causes increases in costs and decreases competition among insurers I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do: * Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice. * Reduce regulations significantly. * In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways: 1. Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices. 2. Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.) Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation. And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers. And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply." https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M @ bcbb3e40:a494e501
2025-03-31 15:44:56El 7 de febrero de 2025, Donald Trump firmó una orden ejecutiva que establecía una «Oficina de la Fe» en la Casa Blanca, dirigida por su asesora espiritual Paula White-Cain, la pastora de esa «teología de la prosperidad» (*prosperity theology*) que predica el «Evangelio de la salud y la riqueza» (*health and wealth gospel[^1]*). Investida de su nueva función, la reverenda pastora dijo: «Tengo la autoridad para declarar a la Casa Blanca un lugar santo. Es mi presencia la que la santifica»[^2]. Los siete rabinos del «Sanedrín Naciente» —la corte suprema que guiará a Israel cuando se reconstruya el Templo de Jerusalén— enviaron conmovedoras felicitaciones al presidente Trump por el establecimiento de esta Oficina. «Expresamos nuestra sincera gratitud —se lee en el mensaje oficial enviado a Trump desde el Monte Sión— por llevar la fe a la vanguardia de la cultura estadounidense y mundial mediante el establecimiento de la Oficina de la Fe en la Casa Blanca. Su reconocimiento de la importancia de la religión en la vida pública es un paso hacia [la restauración de los valores morales y del liderazgo espiritual en el mundo](https://www.hiperbolajanus.com/posts/patriots-mutti/)[^3]. La carta del «Sanedrín Naciente», que augura el éxito a la «misión divina» del presidente estadounidense, reproduce las dos caras de una «moneda del Templo», acuñada en 2017 para celebrar el traslado de la embajada estadounidense a Jerusalén y, simultáneamente, el centenario de la Declaración Balfour. En el anverso se ven los perfiles de Donald Trump y Ciro el Grande, a quien la tradición judía atribuye la reconstrucción del templo destruido por los babilonios, con la inscripción (en hebreo e inglés) «*Cyrus —Balfour— Trump Declaration 1917-2017*»; en el reverso está la imagen del Templo de Jerusalén[^4]. Otra moneda, que lleva los perfiles de Trump y Ciro en el anverso y los de Trump y Netanyahu en el reverso, fue acuñada en 2018 para celebrar el septuagésimo aniversario de la independencia del «Estado de Israel»; se observa dos inscripciones en hebreo e inglés: «Y Él me encargó construirle una casa en Jerusalén» y «Guerra de los Hijos de la Luz contra los Hijos de las Tinieblas». El tema de la «guerra de los Hijos de la Luz contra los Hijos de las Tinieblas» ha tenido una difusión particular en el imaginario y la propaganda trumpista. El 7 de junio de 2020, monseñor Carlo Maria Viganò, ex nuncio de la Santa Sede en los Estados Unidos, escribió una carta al presidente Donald Trump que comenzaba así: «Estamos asistiendo en los últimos meses a la formación de dos bandos, que los definiría bíblicos: los hijos de la luz y los hijos de las tinieblas»[^5]. El 1 de enero de 2021, el agitprop estadounidense Steve Bannon declaró en una entrevista con Monseñor Viganò: «Esta es una batalla de época entre los hijos de la Luz y los hijos de las Tinieblas»[^6]. Son numerosos los judíos sionistas que están en el círculo del presidente Trump: además de su hija Ivanka (convertida en 2009) y su yerno Jared Kushner (entonces Consejero Anciano del Presidente), el 19 de noviembre de 2024 el «The Jerusalem Post»[^7] publicó una lista de los más influyentes: Stephen Miller, subdirector del *staff* de la Casa Blanca y consejero de Seguridad Nacional de Estados Unidos; David Melech Friedman, a quien en 2016 Trump nombró embajador en Israel; el multimillonario «filántropo» Steven Charles Witkoff, enviado especial de Estados Unidos a Oriente Medio; Miriam Adelson, directora del periódico «Israel Hayom», clasificada por *Bloomberg Billionaires* como la quinta mujer más rica del mundo (con un patrimonio neto de 32,400 millones de dólares), financiadora de iniciativas políticas conservadoras en Estados Unidos e Israel; el banquero Boris Epshteyn, consejero estratégico de la campaña presidencial de Trump en 2020; Howard Williams Lutnick, presidente de la *Cantor Fitzgerald* del *Grupo BGC*, financista de las campañas presidenciales de Donald Trump en 2020 y 2024, ahora secretario de Comercio; la modelo Elizabeth Pipko, portavoz nacional del Partido Republicano y creadora de un «museo interactivo virtual» sobre la «Shoah» como parte del proyecto de *Lest People Forget*, cuyo objetivo es combatir el «antisemitismo» y la «negacionismo»; Lee Michael Zeldin, miembro republicano de la Cámara de Representantes por el estado de Nueva York del 2015 al 2023 y actualmente administrador de la EPA (*Environmental Protection Agency*); la columnista Laura Elizabeth Loomer, «orgullosamente islamófoba», activa patrocinadora de Trump en la campaña para las elecciones presidenciales de 2024; Sidney Ferris Rosenberg, influyente presentador de radio y periodista deportivo; William Owen Scharf, Asistente del Presidente y secretario del personal de la Casa Blanca; Marc Jeffrey Rowan, «filántropo» con un patrimonio neto valorado por *Forbes* en ocho mil ochocientos millones de dólares. Además de estos, cabe mencionar al popular presentador de radio Mark Levin quien, en diciembre de 2019, durante la celebración de la fiesta de Janucá en la Casa Blanca, saludó a Donald Trump como «el primer presidente judío de los Estados Unidos»[^8]. Según un funcionario de alto nivel de la Casa Blanca, Donald Trump se convirtió al judaísmo dos años antes en la sinagoga de la secta Jabad Lubavitch en la ciudad de Nueva York. David Elias Goldberg, miembro del *Jewish Center of Antisemitic Study*, también entrevistó al funcionario, para quien «Trump fue “instado” por su hija Ivanka y su yerno Jared Kushner para abrazar la fe. Inicialmente, Trump se habría mostrado reacio, considerando que esto podría enfriar el apoyo del electorado evangélico». Luego, informa «Israel Today News», «cambió de opinión y se convirtió oficialmente a principios de 2017. La ceremonia se llevó a cabo en privado y se guardó celosamente durante casi dos años»[^9]. Pero ya en septiembre de 2015, el rabino millonario Kirt Schneider, invitado a la Trump Tower de Nueva York, había impuesto sus manos sobre la cabeza de Donald Trump y lo había bendecido en hebreo e inglés, declarando: «Las únicas dos naciones que tienen una relación privilegiada con Dios son Israel y los Estados Unidos de América»[^10]. El 7 de octubre de 2024, en el aniversario de la operación de Hamas «Diluvio de Al-Aqsa», Trump fue acompañado por un «superviviente de la Shoah» a la tumba de Menachem Mendel Schneerson, séptimo y último Rabino de los *Hasidim* de la secta Jabad Lubavitch, que en 1991 declaró a sus seguidores: «He hecho todo lo posible para provocar el arribo del Mesías, ahora les paso a ustedes esta misión; hagan todo lo que puedan para que Él venga»[^11]. En relación al evento mesiánico, el eminente rabino Yekutiel Fish atribuyó una misión decisiva a Trump: «Todo el mundo está centrado en Gaza, pero esa es solo una parte de la agenda del fin de los tiempos, que tiene a los judíos viviendo en las fronteras profetizadas de Israel; la Torá incluye explícitamente a Gaza. [Lo que Trump está haciendo es limpiar Gaza de todos los odiadores de Israel](https://www.hiperbolajanus.com/posts/entrevista-mutti-marzo-24/). No podrán estar en Israel después de la venida del Mesías. (...) Esto incluirá a Gaza, la mitad del Líbano y gran parte de Jordania. Y vemos que casi lo hemos logrado. Siria cayó. Líbano está medio destruido. Gaza está destrozada. El escenario está casi listo para el Mesías. Pero, ¿cómo pueden los palestinos estar aquí cuando vayamos a recibir al Mesías? El Mesías necesita que alguien se ocupe de esto, y en este caso, es Donald Trump. Trump está simplemente llevando a cabo las tareas finales necesarias antes de que el Mesías sea revelado»[^12]. Esta inspiración escatológica está presente en las palabras de Pete Brian Hegseth, el pintoresco exponente del «Reconstruccionismo Cristiano»[^13] a quien Trump nombró secretario de Defensa. En un discurso pronunciado en 2019 en el Hotel Rey David de Jerusalén, con motivo de la conferencia anual del canal *Arutz Sheva* (*Israel National News*), Hegseth enalteció el «vínculo eterno» entre Israel y Estados Unidos, y enumeró los «milagros» que atestiguan el «apoyo divino» a la causa sionista, el último de los cuales será la reconstrucción del Templo judío en la zona donde actualmente se encuentra la mezquita de al-Aqsa: «La dignidad de capital adquirida por Jerusalén —dijo— fue un milagro, y no hay razón por la cual no sea posible el milagro de la restauración del Templo en el Monte del Templo».[^14] Es conocido que el fundamentalismo evangélico pro-sionista[^15] comparte con el judaísmo la creencia en que la construcción del tercer Templo de Jerusalén marcará el comienzo de la era mesiánica; cuando la administración Trump trasladó la embajada de Estados Unidos a Jerusalén en 2017, Laurie Cardoza-Moore, exponente del evangelismo sionista, saludó así la «obediencia de Trump a la Palabra de Dios» en «Haaretz»: «Al establecer la Embajada en Jerusalén, el presidente Donald Trump está implementando una de las iniciativas históricas de dimensión bíblica en su presidencia. Al igual que muchos judíos en Israel y en todo el mundo, los cristianos reconocen el vínculo de los judíos con la Biblia a través del nombre de Jerusalén como la capital del antiguo Israel, así como el sitio del Primer y Segundo Templos. Según los profetas Ezequiel, Isaías y el apóstol Juan del Nuevo Testamento, todos los israelíes esperan la reconstrucción del Tercer Templo»[^16]. El 22 de mayo del mismo año, Donald Trump, acompañado de su esposa Melania, de su hija Ivanka y su yerno Jared Kushner, fue el primer presidente de los Estados Unidos en ejercicio en acudir al Muro de las Lamentaciones, anexionado ilegalmente a la entidad sionista. En 2019, la administración Trump confirmó la posición de Estados Unidos al enviar en visita oficial para Jerusalén a Mike Pompeo, un secretario de Estado que —ironía de la Historia— lleva el mismo nombre del general romano que asaltó la ciudad en el año 63 a.C. «Por primera vez en la historia, un secretario de Estado norteamericano visitó la Ciudad Vieja de Jerusalén en compañía de un alto político israelí. Fue una visita histórica que reforzó las expectativas israelíes y constituyó un reconocimiento tácito de la soberanía israelí sobre el sitio del Monte del Templo y la Explanada de las Mezquitas. (…) Mike Pompeo, acompañado por el primer ministro Benjamin Netanyahu y el embajador de Estados Unidos en Israel, David Friedman, también visitó el túnel del Muro de las Lamentaciones y la sinagoga ubicada bajo tierra, en el presunto lugar del santuario del Templo[^17], donde se le mostró una maqueta del futuro Templo[^18]. En el transcurso de una entrevista concedida durante la fiesta del Purim (que celebra el exterminio de la clase política persa, ocurrido hace 2500 años), el secretario de Estado insinuó que «el presidente Donald Trump puede haber sido enviado por Dios para salvar al pueblo judío y que confiaba en que aquí el Señor estaba obrando»[^19]. Como observa Daniele Perra, en este mismo número de «Eurasia», el «mito movilizador» del Tercer Templo, atribuible a los «mitos teológicos» señalados por Roger Garaudy como mitos fundadores de la entidad sionista, «atribuye al judaísmo una especie de función sociológica de transmisión y proyección del conflicto palestino-israelí hacia el resto del mundo y confiere una inspiración apocalíptica al momento geopolítico actual». |**Info**|| |:-|:-| |**Autor**| Claudio Mutti | |**Fuente**| [_I "Figli della Luce" alla Casa Bianca_](https://www.eurasia-rivista.com/i-figli-della-luce-alla-casa-bianca/) | |**Fecha**| 8/Mar/2025 | |**Traducción**| Francisco de la Torre | [^1]: https://en.wikipedia.org/wiki/Prosperity_theology. [^2]: The White House, *President Trump announces appointments to the White House Faith Office* [https://www.whitehouse.gov](https://www.whitehouse.gov/),, 7 de febrero de 2025; *Trump establece la Oficina de la Fe con una foto de «La Última Cena» | Fue dirigida por la controvertida predicadora Paula White*, [https://www.tgcom24.mediaset.it](https://www.tgcom24.mediaset.it/), 10 de febrero de 2025\. [^3]: «We extend our heartfelt gratitude for bringing faith to the forefront of American and global culture through the establishment of the Faith Office in the White House. Your recognition of the importance of religion in public life is a step toward restoring moral values and spiritual leadership in the world» (*Letter from the Nascent Sanhedrin to President Donald J. Trump*, Jerusalem, Wednesday, February 12, 2025). [^4]: *Israeli group mints Trump coin to honor Jerusalem recognition*, «The Times of Israel», [https://www.timesofisrael.com](https://www.timesofisrael.com/), 28-2-2018. [^5]: Mons. Viganò — Siamo nella battaglia tra figli della luce e figli delle tenebre, https://www.italiador.com, 7-6-2020 [^6]: *TRANSCRIPT: Steve Bannon’s ‘War Room’ interview with Abp. Viganò*, lifesitenews.com, 4-1-2021. Sulle origini e sulla fortuna di questo tema cfr. C. Mutti, *Le sètte dell’Occidente*, «Eurasia», 2/2021, pp. 12-15. (https://www.eurasia-rivista.com/las-sectas-de-occidente/) [^7]: Luke Tress, *The who’s who of Jews in Trump’s inner circle?*, «The Jerusalem Post», https://www.jpost.com, 19-11-2024. [^8]: *Radio Talk Show Host Mark Levin Calls President Trump «the First Jewish President of the United States»*, [https://www.c-span.org](https://www.c-span.org/), 11-12-2019. [^9]: «However, he had a change of heart and officially converted in early 2017\. The ceremony was held in private, and closely guarded for nearly two years» (*Donald Trump converted to Judaism two years ago, according to White House official*, https://israeltodaynews.blogspot.com/2019/02). [^10]: «El rabino Kirt Schneider (...) es un millonario judío, una figura televisiva de los “judíos mesiánicos”. Sus emisiones televisivas semanales son emitidas por más de treinta canales cristianos en unos doscientos países; entre ellos, los canales “Yes” y “Hot” en Israel. Solo en Estados Unidos, sus emisiones atraen a 1.600.000 telespectadores cada semana. Kirt Schneider dirige un imperio de telecomunicaciones que tiene un millón y medio de seguidores en Facebook, X (antes Twitter) y YouTube» (Pierre-Antoine Plaquevent — Youssef Hindi, *El milenarismo teopolítico de Israel*, Edizioni all'insegna del Veltro, Parma 2025, p. 31). [^11]: https://it.wikipedia.org/wiki/Menachem_Mendel_Schneerson [^12]: «Everyone is focused on Gaza, but that is only one part of the end-of-days agenda, which has the Jews living in Israel’s prophesied borders. The Torah explicitly includes Gaza. What Trump is doing is cleaning out Gaza of all the haters of Israel. They cannot be in Israel after the Messiah comes. (…) This will include Gaza, half of Lebanon, and much of Jordan. And we see that we are almost there. Syria fell. Lebanon is half gone. Gaza is ripped up. The stage is nearly set for Messiah. But how can the Palestinians be here when we go to greet the Messiah? The Messiah needs someone to take care of this, and in this case, it is Donald Trump. Trump is merely carrying out the final tasks needed before Messiah is revealed» (Adam Eliyahu Berkowitz, *Trump’s Gaza Plan is «The Final task before Messiah»*, [https://israel365news.com](https://israel365news.com/), 5-2-2025). [^13]: «A day after Hegseth was announced for the Cabinet position, Brooks Potteiger, a pastor within the Communion of Reformed Evangelical Churches (CREC), posted on X that Hegseth is a member of the church in good standing. The CREC, a denomination of Christian Reconstructionism, is considered by some academics to be an extremist, Christian supremacist movement» (Shannon Bond e altri, *What’s behind defense secretary pick Hegseth’s war on ‘woke’*, [https://www.npr.org](https://www.npr.org/), 14-11-2024. [^14]: «The decoration of Jerusalem as a capital was a miracle, and there is no reason why the miracle of the re-establishment of Temple on the Temple Mount is not possible» (*Pete Hegseth at Arutz Sheva Conference*, youtube.com). Cfr. Daniele Perra, *Paleotrumpismo, neotrumpismo e post-trumpismo*, in: AA. VV., *Trumpismo*, Cinabro Edizioni, Roma 2025, pp. 22-23. [^15]: Pierre-Antoine Plaquevent — Youssef Hindi, *El milenarismo teopolítico de Israel*, cit., págs. 82 a 96. [^16]: «We American Christians Welcome Trump’s Obedience to God’s Word on Jerusalem», «Haaretz», 6-12-2017. [^17]: Pierre-Antoine Plaquevent — Youssef Hindi, *El milenarismo teopolítico de Israel*, cit., pág. 97. [^18]: *Pompeo en visite historique au mur Occidental aux côtés de Netanyahu et Friedman*, «The Times of Israel», [https://fr.timesofisrael.com](https://fr.timesofisrael.com/), 21-3-2019. [^19]: *Pompeo says Trump may have been sent by God to save Jews from Iran*, «The Times of Israel», 22-3-2019. --- **Artículo original**: Claudio Mutti, [_Los «hijos de la luz» en la Casa Blanca_](https://www.hiperbolajanus.com/posts/hijos-luz-casa-blanca/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/hijos-luz-casa-blanca/), 25/Mar/2025
@ bcbb3e40:a494e501
2025-03-31 15:44:56El 7 de febrero de 2025, Donald Trump firmó una orden ejecutiva que establecía una «Oficina de la Fe» en la Casa Blanca, dirigida por su asesora espiritual Paula White-Cain, la pastora de esa «teología de la prosperidad» (*prosperity theology*) que predica el «Evangelio de la salud y la riqueza» (*health and wealth gospel[^1]*). Investida de su nueva función, la reverenda pastora dijo: «Tengo la autoridad para declarar a la Casa Blanca un lugar santo. Es mi presencia la que la santifica»[^2]. Los siete rabinos del «Sanedrín Naciente» —la corte suprema que guiará a Israel cuando se reconstruya el Templo de Jerusalén— enviaron conmovedoras felicitaciones al presidente Trump por el establecimiento de esta Oficina. «Expresamos nuestra sincera gratitud —se lee en el mensaje oficial enviado a Trump desde el Monte Sión— por llevar la fe a la vanguardia de la cultura estadounidense y mundial mediante el establecimiento de la Oficina de la Fe en la Casa Blanca. Su reconocimiento de la importancia de la religión en la vida pública es un paso hacia [la restauración de los valores morales y del liderazgo espiritual en el mundo](https://www.hiperbolajanus.com/posts/patriots-mutti/)[^3]. La carta del «Sanedrín Naciente», que augura el éxito a la «misión divina» del presidente estadounidense, reproduce las dos caras de una «moneda del Templo», acuñada en 2017 para celebrar el traslado de la embajada estadounidense a Jerusalén y, simultáneamente, el centenario de la Declaración Balfour. En el anverso se ven los perfiles de Donald Trump y Ciro el Grande, a quien la tradición judía atribuye la reconstrucción del templo destruido por los babilonios, con la inscripción (en hebreo e inglés) «*Cyrus —Balfour— Trump Declaration 1917-2017*»; en el reverso está la imagen del Templo de Jerusalén[^4]. Otra moneda, que lleva los perfiles de Trump y Ciro en el anverso y los de Trump y Netanyahu en el reverso, fue acuñada en 2018 para celebrar el septuagésimo aniversario de la independencia del «Estado de Israel»; se observa dos inscripciones en hebreo e inglés: «Y Él me encargó construirle una casa en Jerusalén» y «Guerra de los Hijos de la Luz contra los Hijos de las Tinieblas». El tema de la «guerra de los Hijos de la Luz contra los Hijos de las Tinieblas» ha tenido una difusión particular en el imaginario y la propaganda trumpista. El 7 de junio de 2020, monseñor Carlo Maria Viganò, ex nuncio de la Santa Sede en los Estados Unidos, escribió una carta al presidente Donald Trump que comenzaba así: «Estamos asistiendo en los últimos meses a la formación de dos bandos, que los definiría bíblicos: los hijos de la luz y los hijos de las tinieblas»[^5]. El 1 de enero de 2021, el agitprop estadounidense Steve Bannon declaró en una entrevista con Monseñor Viganò: «Esta es una batalla de época entre los hijos de la Luz y los hijos de las Tinieblas»[^6]. Son numerosos los judíos sionistas que están en el círculo del presidente Trump: además de su hija Ivanka (convertida en 2009) y su yerno Jared Kushner (entonces Consejero Anciano del Presidente), el 19 de noviembre de 2024 el «The Jerusalem Post»[^7] publicó una lista de los más influyentes: Stephen Miller, subdirector del *staff* de la Casa Blanca y consejero de Seguridad Nacional de Estados Unidos; David Melech Friedman, a quien en 2016 Trump nombró embajador en Israel; el multimillonario «filántropo» Steven Charles Witkoff, enviado especial de Estados Unidos a Oriente Medio; Miriam Adelson, directora del periódico «Israel Hayom», clasificada por *Bloomberg Billionaires* como la quinta mujer más rica del mundo (con un patrimonio neto de 32,400 millones de dólares), financiadora de iniciativas políticas conservadoras en Estados Unidos e Israel; el banquero Boris Epshteyn, consejero estratégico de la campaña presidencial de Trump en 2020; Howard Williams Lutnick, presidente de la *Cantor Fitzgerald* del *Grupo BGC*, financista de las campañas presidenciales de Donald Trump en 2020 y 2024, ahora secretario de Comercio; la modelo Elizabeth Pipko, portavoz nacional del Partido Republicano y creadora de un «museo interactivo virtual» sobre la «Shoah» como parte del proyecto de *Lest People Forget*, cuyo objetivo es combatir el «antisemitismo» y la «negacionismo»; Lee Michael Zeldin, miembro republicano de la Cámara de Representantes por el estado de Nueva York del 2015 al 2023 y actualmente administrador de la EPA (*Environmental Protection Agency*); la columnista Laura Elizabeth Loomer, «orgullosamente islamófoba», activa patrocinadora de Trump en la campaña para las elecciones presidenciales de 2024; Sidney Ferris Rosenberg, influyente presentador de radio y periodista deportivo; William Owen Scharf, Asistente del Presidente y secretario del personal de la Casa Blanca; Marc Jeffrey Rowan, «filántropo» con un patrimonio neto valorado por *Forbes* en ocho mil ochocientos millones de dólares. Además de estos, cabe mencionar al popular presentador de radio Mark Levin quien, en diciembre de 2019, durante la celebración de la fiesta de Janucá en la Casa Blanca, saludó a Donald Trump como «el primer presidente judío de los Estados Unidos»[^8]. Según un funcionario de alto nivel de la Casa Blanca, Donald Trump se convirtió al judaísmo dos años antes en la sinagoga de la secta Jabad Lubavitch en la ciudad de Nueva York. David Elias Goldberg, miembro del *Jewish Center of Antisemitic Study*, también entrevistó al funcionario, para quien «Trump fue “instado” por su hija Ivanka y su yerno Jared Kushner para abrazar la fe. Inicialmente, Trump se habría mostrado reacio, considerando que esto podría enfriar el apoyo del electorado evangélico». Luego, informa «Israel Today News», «cambió de opinión y se convirtió oficialmente a principios de 2017. La ceremonia se llevó a cabo en privado y se guardó celosamente durante casi dos años»[^9]. Pero ya en septiembre de 2015, el rabino millonario Kirt Schneider, invitado a la Trump Tower de Nueva York, había impuesto sus manos sobre la cabeza de Donald Trump y lo había bendecido en hebreo e inglés, declarando: «Las únicas dos naciones que tienen una relación privilegiada con Dios son Israel y los Estados Unidos de América»[^10]. El 7 de octubre de 2024, en el aniversario de la operación de Hamas «Diluvio de Al-Aqsa», Trump fue acompañado por un «superviviente de la Shoah» a la tumba de Menachem Mendel Schneerson, séptimo y último Rabino de los *Hasidim* de la secta Jabad Lubavitch, que en 1991 declaró a sus seguidores: «He hecho todo lo posible para provocar el arribo del Mesías, ahora les paso a ustedes esta misión; hagan todo lo que puedan para que Él venga»[^11]. En relación al evento mesiánico, el eminente rabino Yekutiel Fish atribuyó una misión decisiva a Trump: «Todo el mundo está centrado en Gaza, pero esa es solo una parte de la agenda del fin de los tiempos, que tiene a los judíos viviendo en las fronteras profetizadas de Israel; la Torá incluye explícitamente a Gaza. [Lo que Trump está haciendo es limpiar Gaza de todos los odiadores de Israel](https://www.hiperbolajanus.com/posts/entrevista-mutti-marzo-24/). No podrán estar en Israel después de la venida del Mesías. (...) Esto incluirá a Gaza, la mitad del Líbano y gran parte de Jordania. Y vemos que casi lo hemos logrado. Siria cayó. Líbano está medio destruido. Gaza está destrozada. El escenario está casi listo para el Mesías. Pero, ¿cómo pueden los palestinos estar aquí cuando vayamos a recibir al Mesías? El Mesías necesita que alguien se ocupe de esto, y en este caso, es Donald Trump. Trump está simplemente llevando a cabo las tareas finales necesarias antes de que el Mesías sea revelado»[^12]. Esta inspiración escatológica está presente en las palabras de Pete Brian Hegseth, el pintoresco exponente del «Reconstruccionismo Cristiano»[^13] a quien Trump nombró secretario de Defensa. En un discurso pronunciado en 2019 en el Hotel Rey David de Jerusalén, con motivo de la conferencia anual del canal *Arutz Sheva* (*Israel National News*), Hegseth enalteció el «vínculo eterno» entre Israel y Estados Unidos, y enumeró los «milagros» que atestiguan el «apoyo divino» a la causa sionista, el último de los cuales será la reconstrucción del Templo judío en la zona donde actualmente se encuentra la mezquita de al-Aqsa: «La dignidad de capital adquirida por Jerusalén —dijo— fue un milagro, y no hay razón por la cual no sea posible el milagro de la restauración del Templo en el Monte del Templo».[^14] Es conocido que el fundamentalismo evangélico pro-sionista[^15] comparte con el judaísmo la creencia en que la construcción del tercer Templo de Jerusalén marcará el comienzo de la era mesiánica; cuando la administración Trump trasladó la embajada de Estados Unidos a Jerusalén en 2017, Laurie Cardoza-Moore, exponente del evangelismo sionista, saludó así la «obediencia de Trump a la Palabra de Dios» en «Haaretz»: «Al establecer la Embajada en Jerusalén, el presidente Donald Trump está implementando una de las iniciativas históricas de dimensión bíblica en su presidencia. Al igual que muchos judíos en Israel y en todo el mundo, los cristianos reconocen el vínculo de los judíos con la Biblia a través del nombre de Jerusalén como la capital del antiguo Israel, así como el sitio del Primer y Segundo Templos. Según los profetas Ezequiel, Isaías y el apóstol Juan del Nuevo Testamento, todos los israelíes esperan la reconstrucción del Tercer Templo»[^16]. El 22 de mayo del mismo año, Donald Trump, acompañado de su esposa Melania, de su hija Ivanka y su yerno Jared Kushner, fue el primer presidente de los Estados Unidos en ejercicio en acudir al Muro de las Lamentaciones, anexionado ilegalmente a la entidad sionista. En 2019, la administración Trump confirmó la posición de Estados Unidos al enviar en visita oficial para Jerusalén a Mike Pompeo, un secretario de Estado que —ironía de la Historia— lleva el mismo nombre del general romano que asaltó la ciudad en el año 63 a.C. «Por primera vez en la historia, un secretario de Estado norteamericano visitó la Ciudad Vieja de Jerusalén en compañía de un alto político israelí. Fue una visita histórica que reforzó las expectativas israelíes y constituyó un reconocimiento tácito de la soberanía israelí sobre el sitio del Monte del Templo y la Explanada de las Mezquitas. (…) Mike Pompeo, acompañado por el primer ministro Benjamin Netanyahu y el embajador de Estados Unidos en Israel, David Friedman, también visitó el túnel del Muro de las Lamentaciones y la sinagoga ubicada bajo tierra, en el presunto lugar del santuario del Templo[^17], donde se le mostró una maqueta del futuro Templo[^18]. En el transcurso de una entrevista concedida durante la fiesta del Purim (que celebra el exterminio de la clase política persa, ocurrido hace 2500 años), el secretario de Estado insinuó que «el presidente Donald Trump puede haber sido enviado por Dios para salvar al pueblo judío y que confiaba en que aquí el Señor estaba obrando»[^19]. Como observa Daniele Perra, en este mismo número de «Eurasia», el «mito movilizador» del Tercer Templo, atribuible a los «mitos teológicos» señalados por Roger Garaudy como mitos fundadores de la entidad sionista, «atribuye al judaísmo una especie de función sociológica de transmisión y proyección del conflicto palestino-israelí hacia el resto del mundo y confiere una inspiración apocalíptica al momento geopolítico actual». |**Info**|| |:-|:-| |**Autor**| Claudio Mutti | |**Fuente**| [_I "Figli della Luce" alla Casa Bianca_](https://www.eurasia-rivista.com/i-figli-della-luce-alla-casa-bianca/) | |**Fecha**| 8/Mar/2025 | |**Traducción**| Francisco de la Torre | [^1]: https://en.wikipedia.org/wiki/Prosperity_theology. [^2]: The White House, *President Trump announces appointments to the White House Faith Office* [https://www.whitehouse.gov](https://www.whitehouse.gov/),, 7 de febrero de 2025; *Trump establece la Oficina de la Fe con una foto de «La Última Cena» | Fue dirigida por la controvertida predicadora Paula White*, [https://www.tgcom24.mediaset.it](https://www.tgcom24.mediaset.it/), 10 de febrero de 2025\. [^3]: «We extend our heartfelt gratitude for bringing faith to the forefront of American and global culture through the establishment of the Faith Office in the White House. Your recognition of the importance of religion in public life is a step toward restoring moral values and spiritual leadership in the world» (*Letter from the Nascent Sanhedrin to President Donald J. Trump*, Jerusalem, Wednesday, February 12, 2025). [^4]: *Israeli group mints Trump coin to honor Jerusalem recognition*, «The Times of Israel», [https://www.timesofisrael.com](https://www.timesofisrael.com/), 28-2-2018. [^5]: Mons. Viganò — Siamo nella battaglia tra figli della luce e figli delle tenebre, https://www.italiador.com, 7-6-2020 [^6]: *TRANSCRIPT: Steve Bannon’s ‘War Room’ interview with Abp. Viganò*, lifesitenews.com, 4-1-2021. Sulle origini e sulla fortuna di questo tema cfr. C. Mutti, *Le sètte dell’Occidente*, «Eurasia», 2/2021, pp. 12-15. (https://www.eurasia-rivista.com/las-sectas-de-occidente/) [^7]: Luke Tress, *The who’s who of Jews in Trump’s inner circle?*, «The Jerusalem Post», https://www.jpost.com, 19-11-2024. [^8]: *Radio Talk Show Host Mark Levin Calls President Trump «the First Jewish President of the United States»*, [https://www.c-span.org](https://www.c-span.org/), 11-12-2019. [^9]: «However, he had a change of heart and officially converted in early 2017\. The ceremony was held in private, and closely guarded for nearly two years» (*Donald Trump converted to Judaism two years ago, according to White House official*, https://israeltodaynews.blogspot.com/2019/02). [^10]: «El rabino Kirt Schneider (...) es un millonario judío, una figura televisiva de los “judíos mesiánicos”. Sus emisiones televisivas semanales son emitidas por más de treinta canales cristianos en unos doscientos países; entre ellos, los canales “Yes” y “Hot” en Israel. Solo en Estados Unidos, sus emisiones atraen a 1.600.000 telespectadores cada semana. Kirt Schneider dirige un imperio de telecomunicaciones que tiene un millón y medio de seguidores en Facebook, X (antes Twitter) y YouTube» (Pierre-Antoine Plaquevent — Youssef Hindi, *El milenarismo teopolítico de Israel*, Edizioni all'insegna del Veltro, Parma 2025, p. 31). [^11]: https://it.wikipedia.org/wiki/Menachem_Mendel_Schneerson [^12]: «Everyone is focused on Gaza, but that is only one part of the end-of-days agenda, which has the Jews living in Israel’s prophesied borders. The Torah explicitly includes Gaza. What Trump is doing is cleaning out Gaza of all the haters of Israel. They cannot be in Israel after the Messiah comes. (…) This will include Gaza, half of Lebanon, and much of Jordan. And we see that we are almost there. Syria fell. Lebanon is half gone. Gaza is ripped up. The stage is nearly set for Messiah. But how can the Palestinians be here when we go to greet the Messiah? The Messiah needs someone to take care of this, and in this case, it is Donald Trump. Trump is merely carrying out the final tasks needed before Messiah is revealed» (Adam Eliyahu Berkowitz, *Trump’s Gaza Plan is «The Final task before Messiah»*, [https://israel365news.com](https://israel365news.com/), 5-2-2025). [^13]: «A day after Hegseth was announced for the Cabinet position, Brooks Potteiger, a pastor within the Communion of Reformed Evangelical Churches (CREC), posted on X that Hegseth is a member of the church in good standing. The CREC, a denomination of Christian Reconstructionism, is considered by some academics to be an extremist, Christian supremacist movement» (Shannon Bond e altri, *What’s behind defense secretary pick Hegseth’s war on ‘woke’*, [https://www.npr.org](https://www.npr.org/), 14-11-2024. [^14]: «The decoration of Jerusalem as a capital was a miracle, and there is no reason why the miracle of the re-establishment of Temple on the Temple Mount is not possible» (*Pete Hegseth at Arutz Sheva Conference*, youtube.com). Cfr. Daniele Perra, *Paleotrumpismo, neotrumpismo e post-trumpismo*, in: AA. VV., *Trumpismo*, Cinabro Edizioni, Roma 2025, pp. 22-23. [^15]: Pierre-Antoine Plaquevent — Youssef Hindi, *El milenarismo teopolítico de Israel*, cit., págs. 82 a 96. [^16]: «We American Christians Welcome Trump’s Obedience to God’s Word on Jerusalem», «Haaretz», 6-12-2017. [^17]: Pierre-Antoine Plaquevent — Youssef Hindi, *El milenarismo teopolítico de Israel*, cit., pág. 97. [^18]: *Pompeo en visite historique au mur Occidental aux côtés de Netanyahu et Friedman*, «The Times of Israel», [https://fr.timesofisrael.com](https://fr.timesofisrael.com/), 21-3-2019. [^19]: *Pompeo says Trump may have been sent by God to save Jews from Iran*, «The Times of Israel», 22-3-2019. --- **Artículo original**: Claudio Mutti, [_Los «hijos de la luz» en la Casa Blanca_](https://www.hiperbolajanus.com/posts/hijos-luz-casa-blanca/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/hijos-luz-casa-blanca/), 25/Mar/2025 @ 91bea5cd:1df4451c
2025-02-04 17:24:50### Definição de ULID: Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível. #### Gerar ULID ```sql CREATE EXTENSION IF NOT EXISTS pgcrypto; CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\\000\\000\\000\\000\\000\\000'; output TEXT = ''; unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER); -- 10 entropy bytes ulid = timestamp || gen_random_bytes(10); -- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31))); -- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31))); RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ``` #### ULID TO UUID ```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF; v = regexp_split_to_array(ulid, ''); -- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]); -- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]); RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE; CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ``` #### UUID to ULID ```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN -- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31))); -- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31))); RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ``` #### Gera 11 Digitos aleatórios: YBKXG0CKTH4 ```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT; -- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars; END; $$ LANGUAGE plpgsql; ``` #### Exemplo de USO ```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL ); -- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ``` ### Fontes - https://github.com/scoville/pgsql-ulid - https://github.com/geckoboard/pgulid
@ 91bea5cd:1df4451c
2025-02-04 17:24:50### Definição de ULID: Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível. #### Gerar ULID ```sql CREATE EXTENSION IF NOT EXISTS pgcrypto; CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\\000\\000\\000\\000\\000\\000'; output TEXT = ''; unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER); -- 10 entropy bytes ulid = timestamp || gen_random_bytes(10); -- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31))); -- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31))); RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ``` #### ULID TO UUID ```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF; v = regexp_split_to_array(ulid, ''); -- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]); -- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]); RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE; CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ``` #### UUID to ULID ```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN -- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31))); -- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31))); RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ``` #### Gera 11 Digitos aleatórios: YBKXG0CKTH4 ```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT; -- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars; END; $$ LANGUAGE plpgsql; ``` #### Exemplo de USO ```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL ); -- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ``` ### Fontes - https://github.com/scoville/pgsql-ulid - https://github.com/geckoboard/pgulid @ bcbb3e40:a494e501
2025-03-31 15:34:12|[](https://www.hiperbolajanus.com/libros/thiriart-joven-europa-missiaggia/)| |:-:| |[MISSIAGGIA, Pietro; _Jean Thiriart, el caballero euroasiático y la Joven Europa_; Hipérbola Janus, 2025](https://www.hiperbolajanus.com/libros/thiriart-joven-europa-missiaggia/)| Desde nuestros inicios los autores y temáticas relacionadas con la geopolítica nos han procurado atención e interés por parte del gran público y de los *mass media*, y no hay más que recordar el efecto que han venido teniendo nuestras obras de [**Aleksandr Duguin**](https://hiperbolajanus.com/firmas/aleksandr-g.-duguin/), en especial [*La geopolítica de Rusia*](https://hiperbolajanus.com/libros/geopolitica-rusia-aleksandr-duguin/) y [*Proyecto Eurasia: teoría y praxis*](https://hiperbolajanus.com/libros/proyecto-eurasia-aleksandr-duguin/), sobre todo a raíz de [nuestra presentación en Casa de Rusia](https://youtu.be/rsp-FMmSPJE) en un ya lejano 2016, con la inestimable colaboración de [**Jordi de la Fuente**](https://hiperbolajanus.com/firmas/jordi-de-la-fuente-miro/) como prologuista, trabajo que siempre reivindicamos desde nuestros medios por el prestigio, la calidad y brillantez de exposición del mismo. Más allá de las obras del prestigioso y afamado filósofo y politólogo ruso, también hemos realizado otras incursiones en esta vertiente, que podríamos llamar «geopolítica alternativa», introduciendo las obras de otros notables autores como [**Claudio Mutti**](https://amzn.to/3RfXOUZ), [**Carlo Terracciano**](https://amzn.to/4iq9mkA) o [**Boris Nad**](https://amzn.to/3Fv98tT). Con estos autores hemos tratado de profundizar en esa vía que se opone frontalmente, y radicalmente si se quiere, a los planteamientos derivados de la geopolítica atlantista y liberal que tiene su principal polo en Estados Unidos, haciendo especial hincapié en el subyugamiento que vienen ejerciendo desde 1945 en adelante respecto a una Europa convertida en un protectorado en una mera colonia. Es por este motivo por el que la publicación de _Jean Thiriart, el caballero euroasiático y la Joven Europa_ nos parece una obra totalmente pertinente en estos momentos, forma parte del desarrollo lógico de la línea editorial en la que estamos encauzados desde nuestros inicios, y viene a representar una de las múltiples vías en las que confluye la idea, [profundamente schmittiana](https://hiperbolajanus.com/posts/tierra-mar-katechon/), de la política de los grandes espacios. En este caso la idea de una Europa unida, bajo un vasto proyecto que traspasa los estrechos límites del continente concebido como un apéndice más del [«Occidente», de ese subproducto ideológico decadente y funcional a los intereses del otro lado del Atlántico](https://hiperbolajanus.com/posts/presentacion-despues-virus-boris-nad/). Para comprender la idea de una Europa unida, que comprenda a Rusia, y su enorme extensión territorial a lo largo de 17 millones de kilómetros cuadrados, y la importancia estratégica de su ubicación, es necesario recurrir al legado de **Jean Thiriart**, conocer su obra, pero también al hombre, pues una no se comprende sin el otro, en este caso hablamos de elementos correlativos. || |:-:| |Jean Thiriart (1922-1992)| ¿Pero quién fue Jean Thiriart? Esta obra nos permite adentrarnos en aspectos biográficos, algunos de ellos poco conocidos para el gran público de habla hispana, y saber de su trayectoria, de la maduración de sus ideas, de su proyecto político y de las etapas que componen el desarrollo del mismo y que aparecen claramente diferenciadas: hablamos del proyecto político de unidad europea, que alcanza su concreción teórica en *¡Arriba Europa!: Una Europa unida: un imperio de 400 millones de hombres* (1965, Editorial Mateu, Barcelona), en pleno apogeo de la organización *Jeune Europe*, que se convirtió en el órgano político a partir del cual creyó poder implementar su proyecto unitario a escala europeo, manteniendo una posición de independencia respecto a los dos pretendidos bloques antagónicos de Guerra Fría: Estados Unidos y la Unión Soviética. En esa época, estamos hablando del ecuador de los años 60, [todo el mundo de la Contracultura](https://hiperbolajanus.com/posts/mito-contracultura/), falsamente contestatario, estaba articulando su propio discurso, que tendría su expresión más nítida a través del ya conocido Mayo del 68 francés o la Primavera de Praga, durante el mismo año. Y si el movimiento de Nueva Derecha liderado por **Alain de Benoist** surgiría en lo sucesivo, ya en la década de los años 70, como una «reacción» frente a la «rebelión contracultural», no podemos obviar la importancia de un movimiento político como *Jeune Europe*, una organización política transnacional, a escala de la Europa occidental, con sus diferentes delegaciones en países como Francia, Italia, Alemania, la propia España además de, como es obvio, Bélgica, país de origen de nuestro autor. Jean Thiriart ha sido etiquetado con reiteración como un político y teórico de «extrema derecha», se han hecho numerosos discursos interesados para vincularlo, por cuestiones de orden biográfico muy circunscritas a determinado periodo, con el fascismo y el nacionalsocialismo de entreguerras. Sin embargo, y como el lector podrá descubrir a lo largo de la presente obra, el pensamiento de nuestro autor está muy lejos de ser reducible a meras etiquetas, y en ningún caso mostró las filiaciones que se le atribuyen desde posicionamientos ideológicos, sino que, muy al contrario, vemos a un hombre de pensamiento racional y pragmático, poderosamente influenciado por la geopolítica y abierto a alianzas estratégicas más variadas, más allá de todo fundamentalismo ideológico. Es por este motivo que veremos a un Thiriart buscando sinergias y entendimiento entre círculos de izquierdas, antiimperialistas en una lucha concebida como «cuatricontinental». No en vano, muchos de los cuadros políticos que se formaron en *Giovane Europa*, la rama italiana, terminaron por militar incluso en organizaciones de extrema izquierda de inspiración maoísta. En el caso de España hubo un notable apoyo a la organización por parte de los falangistas más disidentes. De manera que Jean Thiriart representa una figura política compleja, con influencias variadas, que van desde los hermanos **Strasser**, pasando por **Ernst Niekish** o **Vilfredo Pareto**, e incluso, por **Sieyès** o **Robespierre**. Es a partir de *Jeune Europe* cuando el nacionalismo europeo, la idea de una Europa unida desde Brest a Bucarest toma cuerpo. En la obra mencionada con anterioridad (*¡Arriba Europa!: Una Europa unida: un imperio de 400 millones de hombres*) Jean Thiriart ya nos presenta a través de unos trazos muy definidos el proyecto del comunitarismo nacional-europeo, la piedra angular de su proyecto político. La idea de un socialismo aristocrático y europeo, trascendiendo las fronteras del Estado-nación liberal decimonónico, y los particularismos nacionales, concebidos como formas obsoletas y «estrechas de miras», obstáculos a superar en la convergencia del Imperio europeo. Porque vemos a un Thiriart que potencia la estructura del Estado, del aparato de poder, tratando de potenciar, y restaurar naturalmente, el papel y la preponderancia de Europa como espacio de civilización en el mundo. Es un nacionalismo europeo que viene determinado por razones puramente geopolíticas, algo que también fue objeto de críticas, concretamente por parte del geopolítico austriaco **Heinrich von Lohausen**, y que también recogemos en el presente volúmen de la obra. || |:-:| |Ejemplar de una de las publicaciones más importantes de Joven Europa (Jeune Europe) cuya portada refleja el antiamericanismo y antiimperialismo característicos del nacionalismo europeo de la organización.| En este sentido, Thiriart no andaba nada desencaminado, en la medida que pensaba que solo los Estados de dimensiones continentales podrían ser capaces de defender su independencia y soberanía, y ejercer un poder en el mundo, frente a los antiguos nacionalismos europeos, totalmente anacrónicos y un factor de ruptura y desintegración del potencial europeo. En este contexto, se hace necesario eliminar el orden establecido en Yalta en 1945, que convierte a Europa en un vasallo de las grandes potencias vencedoras de la Segunda Guerra Mundial. De modo que luchar contra la ocupación estadounidense por un lado, y soviética por otro lado, fuese el principal *leitmotiv* del Partido Revolucionario Europeo, un partido histórico señala Thiriart, encargado de llevar a término la acción unificadora continental. Y es con este propósito con el que se tratan de concertar una serie de alianzas internacionales que llevó a Thiriart y su organización a tratar con personal diplomático y gubernamental de los países árabes no alineados, del régimen de **Fidel Castro** o incluso con emisarios del gobierno chino, como ocurrió en el famoso encuentro propiciado por **Ceaucescu** en Bucarest con **Zhou En-Lai**. Quizás, uno de los puntos donde más desacuerdos encontramos con las teorías thiriartianas se encuentra en ciertos fundamentos que la articulan, en un modelo racionalista, materialista y pragmático, de hecho no debemos olvidar que **Maquiavelo** era uno de sus referentes, y con éste la posterior hornada de autores neomaquiavélicos como Vilfredo Pareto. El excesivo pragmatismo de sus planteamientos, un estatalismo exacerbado y sin concesiones a las particularidades de los pueblos, una suerte de centralismo jacobino, y la ausencia de un elemento trascendente capaz de dar una justificación metafísica a todo el proyecto nacional europeo constituyen, en nuestra opinión, una parte discutible y reformulable. En otro terreno, como pueda ser el puramente económico, encontramos un proyecto anticapitalista en muchos de sus aspectos, frente al democratismo parlamentario liberal, y apoyándose en las teorías económicas de **Johann G. Fichte** o **Friedrich List**, rechazando cualquier organización económica transnacional que pueda mediatizar o convertir a Europa en objeto de sus actividades usurocráticas y depredatorias, colocando la soberanía e independencia económica europea en una de las máximas prioridades en este terreno. Debemos destacar, porque es un elemento de debate especialmente interesante, el apartado del libro que se corresponde al escrito de **Luc Michel**, publicado en Italia bajo el título *Da Jeune Europe alle Brigate Rosse*, en el libro *Parte II Historia de Jeune Europe (1962-1969)*, en el que se detallan las colaboraciones que comenzaron a sucederse entre la militancia de la delegación italiana, *Giovane Europa*, y círculos de extrema izquierda maoísta, y cómo muchos de los antiguos militantes nacional-europeos terminaron militando en organizaciones de esta facción ideológica, y nos referimos a casos tan representativos en la época como **Claudio Orsoni** o **Pino Bolzano** entre otros muchos. La actividad proselitista de *Jeune Europe* en el último lustro de la década de los años 60, con la fundación del Partido Comunitario Europeo, nos legó una gran cantidad de publicaciones, entre las cuales destacaron *La Nation Européenne*, *La Nazione Europea* o *Europa Combattente*, cuyas portadas han servido para ilustrar las páginas interiores de nuestra obra, y que procuraron una actividad proselitista y de difusión de ideas que llegaron a imprimir semanal y mensualmente varios miles de ejemplares en Francia o en Italia. Tras agotar todas las vías posibles de alianzas y convergencias, con encuentros poco afortunados, vemos a un Thiriart que prefiere adoptar otras vías para seguir construyendo el proyecto nacional-europeo más allá de la fórmula activista y del partido político. Este es el motivo por el cual, en los siguientes años, ya en la última etapa de su vida, veremos esa transición del político activista al teórico y al ideólogo como parte de una nueva estrategia dentro del proyecto político al que consagró buena parte de su vida, y es un hecho que comienza a apreciarse desde mediados de los años 70. Durante esta época la «Europa de Brest a Bucarest» se transforma y amplía en una «Europa desde Dublín a Vladivostok». Thiriart aborda ya abiertamente la integración del espacio soviético en una Europa unida que abarca un inmenso espacio territorial, capaz de unir el Océano Atlántico y el Océano Pacífico de un extremo a otro, el «Imperio Eurosoviético». No obstante, Thiriart siempre piensa en términos geopolíticos, y considera que este proceso de integración debe llevarse a cabo desde una revisión de la ideología soviética, desde una marcada desmarxistización de su socialismo, purgado de todo dogmatismo y elementos condicionantes derivados de la teoría del Estado formulada por el marxismo-leninismo para tomar en su lugar aquella de **Thomas Hobbes**. A partir de este momento solamente hay un enemigo, el que representa el poder estadounidense y el dominio que éste ejerce sobre la Europa occidental. A partir de ese momento la URSS, bajo las premisas apuntadas por Thiriart, y desde una ideología soviética «desmarxistizada», es la que debe asumir el proyecto de integración europea. Todo este enfoque terminará conociendo su colofón final al final de la vida de Jean Thiriart, cuando éste se encuentre ya en sus último año de vida, en 1992, con una Unión Soviética ya periclitada y disuelta, con un país sumido en una crisis económica, política y social bajo el gobierno decadente de **Yeltsin**, con un poder notablemente menguado y a merced de las potencias extranjeras y las apetencias de las organizaciones financieras transnacionales. En este contexto tendrá lugar el conocido viaje de Jean Thiriart a Moscú, donde se encontrará, además de con la disidencia de Yeltsin, encabezada por el Partido Comunista dirigido por **Gennadij Ziuganov** y numerosas personalidades públicas del ámbito ruso, entre las que destacará por encima de todos el filósofo y politólogo **Aleksandr Duguin**, quien en la presente obra también reivindica la figura del belga como un contribuidor directo del [pensamiento euroasiático](https://amzn.to/3FsF3Lr). Además de medios de prensa, políticos e intelectuales rusos, nuestro autor también compartirá espacio con una pequeña delegación de la revista italiana «Orion», especializada en temática geopolítica, y representada por el padre de la geopolítica italiana, Carlo Terracciano. El encuentro no tendrá mayores consecuencias, y vendrá a significar el último acto de servicio de Jean Thiriart en su denodado esfuerzo por lograr la integración de Europa y Rusia en un poderoso bloque geopolítico capaz de hacer frente a la hegemonía estadounidense en el mundo. Terminaremos este breve y sintético escrito de presentación con un fragmento de la obra que Jean Thiriart publicó en 1965 bajo el título *¡Arriba Europa!: Una Europa unida: un imperio de 400 millones de hombres*, que nos parece de lo más adecuado para poner el punto final al presente texto: > Europa, este **MILAGRO** en la historia del hombre, este milagro que siguió al milagro griego, ha dado vida, con la prodigiosa fecundidad de su civilización irrepetible, a una cultura adoptada por el mundo entero. En la competencia surgida entre las grandes civilizaciones —occidental, india, china y japonesa— la nuestra ha aplastado a las demás. > > La **civilización** es creadora de cultura. La cultura, en cambio, jamás ha creado civilización. > > **SOLO** Europa posee la civilización; de ahí deriva su supremacía sobre los Estados Unidos y la Rusia comunista, que poseen únicamente la cultura nacida de nuestra civilización, como ha demostrado magistralmente Oswald Spengler. > > Esta cultura, separada de su civilización, está condenada a la esterilidad, la cual se manifestará primero mediante una esclerosis y, posteriormente, mediante un retorno a la barbarie. > > Políticamente dominada por Moscú o por Washington, la civilización europea se ve asfixiada y corre el riesgo de estancarse en su estado de simple cultura. Basta notar que todos los descubrimientos en el campo nuclear y astronáutico son obra de europeos. Todos buscan a los científicos europeos. > > Solo una Europa políticamente unida puede proveer los medios de poder que garantizarán las condiciones históricas indispensables para la supervivencia de esta civilización. > > Ninguna otra potencia, por otra parte, podría sustituir a Europa en su misión hacia la humanidad. --- **Artículo original**: Hipérbola Janus, [_Presentación de «Jean Thiriart, el caballero euroasiático y la Joven Europa», de Pietro Missiaggia_](https://www.hiperbolajanus.com/posts/presentacion-thiriart-missiaggia/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/presentacion-thiriart-missiaggia/), 18/Mar/2025
@ bcbb3e40:a494e501
2025-03-31 15:34:12|[](https://www.hiperbolajanus.com/libros/thiriart-joven-europa-missiaggia/)| |:-:| |[MISSIAGGIA, Pietro; _Jean Thiriart, el caballero euroasiático y la Joven Europa_; Hipérbola Janus, 2025](https://www.hiperbolajanus.com/libros/thiriart-joven-europa-missiaggia/)| Desde nuestros inicios los autores y temáticas relacionadas con la geopolítica nos han procurado atención e interés por parte del gran público y de los *mass media*, y no hay más que recordar el efecto que han venido teniendo nuestras obras de [**Aleksandr Duguin**](https://hiperbolajanus.com/firmas/aleksandr-g.-duguin/), en especial [*La geopolítica de Rusia*](https://hiperbolajanus.com/libros/geopolitica-rusia-aleksandr-duguin/) y [*Proyecto Eurasia: teoría y praxis*](https://hiperbolajanus.com/libros/proyecto-eurasia-aleksandr-duguin/), sobre todo a raíz de [nuestra presentación en Casa de Rusia](https://youtu.be/rsp-FMmSPJE) en un ya lejano 2016, con la inestimable colaboración de [**Jordi de la Fuente**](https://hiperbolajanus.com/firmas/jordi-de-la-fuente-miro/) como prologuista, trabajo que siempre reivindicamos desde nuestros medios por el prestigio, la calidad y brillantez de exposición del mismo. Más allá de las obras del prestigioso y afamado filósofo y politólogo ruso, también hemos realizado otras incursiones en esta vertiente, que podríamos llamar «geopolítica alternativa», introduciendo las obras de otros notables autores como [**Claudio Mutti**](https://amzn.to/3RfXOUZ), [**Carlo Terracciano**](https://amzn.to/4iq9mkA) o [**Boris Nad**](https://amzn.to/3Fv98tT). Con estos autores hemos tratado de profundizar en esa vía que se opone frontalmente, y radicalmente si se quiere, a los planteamientos derivados de la geopolítica atlantista y liberal que tiene su principal polo en Estados Unidos, haciendo especial hincapié en el subyugamiento que vienen ejerciendo desde 1945 en adelante respecto a una Europa convertida en un protectorado en una mera colonia. Es por este motivo por el que la publicación de _Jean Thiriart, el caballero euroasiático y la Joven Europa_ nos parece una obra totalmente pertinente en estos momentos, forma parte del desarrollo lógico de la línea editorial en la que estamos encauzados desde nuestros inicios, y viene a representar una de las múltiples vías en las que confluye la idea, [profundamente schmittiana](https://hiperbolajanus.com/posts/tierra-mar-katechon/), de la política de los grandes espacios. En este caso la idea de una Europa unida, bajo un vasto proyecto que traspasa los estrechos límites del continente concebido como un apéndice más del [«Occidente», de ese subproducto ideológico decadente y funcional a los intereses del otro lado del Atlántico](https://hiperbolajanus.com/posts/presentacion-despues-virus-boris-nad/). Para comprender la idea de una Europa unida, que comprenda a Rusia, y su enorme extensión territorial a lo largo de 17 millones de kilómetros cuadrados, y la importancia estratégica de su ubicación, es necesario recurrir al legado de **Jean Thiriart**, conocer su obra, pero también al hombre, pues una no se comprende sin el otro, en este caso hablamos de elementos correlativos. || |:-:| |Jean Thiriart (1922-1992)| ¿Pero quién fue Jean Thiriart? Esta obra nos permite adentrarnos en aspectos biográficos, algunos de ellos poco conocidos para el gran público de habla hispana, y saber de su trayectoria, de la maduración de sus ideas, de su proyecto político y de las etapas que componen el desarrollo del mismo y que aparecen claramente diferenciadas: hablamos del proyecto político de unidad europea, que alcanza su concreción teórica en *¡Arriba Europa!: Una Europa unida: un imperio de 400 millones de hombres* (1965, Editorial Mateu, Barcelona), en pleno apogeo de la organización *Jeune Europe*, que se convirtió en el órgano político a partir del cual creyó poder implementar su proyecto unitario a escala europeo, manteniendo una posición de independencia respecto a los dos pretendidos bloques antagónicos de Guerra Fría: Estados Unidos y la Unión Soviética. En esa época, estamos hablando del ecuador de los años 60, [todo el mundo de la Contracultura](https://hiperbolajanus.com/posts/mito-contracultura/), falsamente contestatario, estaba articulando su propio discurso, que tendría su expresión más nítida a través del ya conocido Mayo del 68 francés o la Primavera de Praga, durante el mismo año. Y si el movimiento de Nueva Derecha liderado por **Alain de Benoist** surgiría en lo sucesivo, ya en la década de los años 70, como una «reacción» frente a la «rebelión contracultural», no podemos obviar la importancia de un movimiento político como *Jeune Europe*, una organización política transnacional, a escala de la Europa occidental, con sus diferentes delegaciones en países como Francia, Italia, Alemania, la propia España además de, como es obvio, Bélgica, país de origen de nuestro autor. Jean Thiriart ha sido etiquetado con reiteración como un político y teórico de «extrema derecha», se han hecho numerosos discursos interesados para vincularlo, por cuestiones de orden biográfico muy circunscritas a determinado periodo, con el fascismo y el nacionalsocialismo de entreguerras. Sin embargo, y como el lector podrá descubrir a lo largo de la presente obra, el pensamiento de nuestro autor está muy lejos de ser reducible a meras etiquetas, y en ningún caso mostró las filiaciones que se le atribuyen desde posicionamientos ideológicos, sino que, muy al contrario, vemos a un hombre de pensamiento racional y pragmático, poderosamente influenciado por la geopolítica y abierto a alianzas estratégicas más variadas, más allá de todo fundamentalismo ideológico. Es por este motivo que veremos a un Thiriart buscando sinergias y entendimiento entre círculos de izquierdas, antiimperialistas en una lucha concebida como «cuatricontinental». No en vano, muchos de los cuadros políticos que se formaron en *Giovane Europa*, la rama italiana, terminaron por militar incluso en organizaciones de extrema izquierda de inspiración maoísta. En el caso de España hubo un notable apoyo a la organización por parte de los falangistas más disidentes. De manera que Jean Thiriart representa una figura política compleja, con influencias variadas, que van desde los hermanos **Strasser**, pasando por **Ernst Niekish** o **Vilfredo Pareto**, e incluso, por **Sieyès** o **Robespierre**. Es a partir de *Jeune Europe* cuando el nacionalismo europeo, la idea de una Europa unida desde Brest a Bucarest toma cuerpo. En la obra mencionada con anterioridad (*¡Arriba Europa!: Una Europa unida: un imperio de 400 millones de hombres*) Jean Thiriart ya nos presenta a través de unos trazos muy definidos el proyecto del comunitarismo nacional-europeo, la piedra angular de su proyecto político. La idea de un socialismo aristocrático y europeo, trascendiendo las fronteras del Estado-nación liberal decimonónico, y los particularismos nacionales, concebidos como formas obsoletas y «estrechas de miras», obstáculos a superar en la convergencia del Imperio europeo. Porque vemos a un Thiriart que potencia la estructura del Estado, del aparato de poder, tratando de potenciar, y restaurar naturalmente, el papel y la preponderancia de Europa como espacio de civilización en el mundo. Es un nacionalismo europeo que viene determinado por razones puramente geopolíticas, algo que también fue objeto de críticas, concretamente por parte del geopolítico austriaco **Heinrich von Lohausen**, y que también recogemos en el presente volúmen de la obra. || |:-:| |Ejemplar de una de las publicaciones más importantes de Joven Europa (Jeune Europe) cuya portada refleja el antiamericanismo y antiimperialismo característicos del nacionalismo europeo de la organización.| En este sentido, Thiriart no andaba nada desencaminado, en la medida que pensaba que solo los Estados de dimensiones continentales podrían ser capaces de defender su independencia y soberanía, y ejercer un poder en el mundo, frente a los antiguos nacionalismos europeos, totalmente anacrónicos y un factor de ruptura y desintegración del potencial europeo. En este contexto, se hace necesario eliminar el orden establecido en Yalta en 1945, que convierte a Europa en un vasallo de las grandes potencias vencedoras de la Segunda Guerra Mundial. De modo que luchar contra la ocupación estadounidense por un lado, y soviética por otro lado, fuese el principal *leitmotiv* del Partido Revolucionario Europeo, un partido histórico señala Thiriart, encargado de llevar a término la acción unificadora continental. Y es con este propósito con el que se tratan de concertar una serie de alianzas internacionales que llevó a Thiriart y su organización a tratar con personal diplomático y gubernamental de los países árabes no alineados, del régimen de **Fidel Castro** o incluso con emisarios del gobierno chino, como ocurrió en el famoso encuentro propiciado por **Ceaucescu** en Bucarest con **Zhou En-Lai**. Quizás, uno de los puntos donde más desacuerdos encontramos con las teorías thiriartianas se encuentra en ciertos fundamentos que la articulan, en un modelo racionalista, materialista y pragmático, de hecho no debemos olvidar que **Maquiavelo** era uno de sus referentes, y con éste la posterior hornada de autores neomaquiavélicos como Vilfredo Pareto. El excesivo pragmatismo de sus planteamientos, un estatalismo exacerbado y sin concesiones a las particularidades de los pueblos, una suerte de centralismo jacobino, y la ausencia de un elemento trascendente capaz de dar una justificación metafísica a todo el proyecto nacional europeo constituyen, en nuestra opinión, una parte discutible y reformulable. En otro terreno, como pueda ser el puramente económico, encontramos un proyecto anticapitalista en muchos de sus aspectos, frente al democratismo parlamentario liberal, y apoyándose en las teorías económicas de **Johann G. Fichte** o **Friedrich List**, rechazando cualquier organización económica transnacional que pueda mediatizar o convertir a Europa en objeto de sus actividades usurocráticas y depredatorias, colocando la soberanía e independencia económica europea en una de las máximas prioridades en este terreno. Debemos destacar, porque es un elemento de debate especialmente interesante, el apartado del libro que se corresponde al escrito de **Luc Michel**, publicado en Italia bajo el título *Da Jeune Europe alle Brigate Rosse*, en el libro *Parte II Historia de Jeune Europe (1962-1969)*, en el que se detallan las colaboraciones que comenzaron a sucederse entre la militancia de la delegación italiana, *Giovane Europa*, y círculos de extrema izquierda maoísta, y cómo muchos de los antiguos militantes nacional-europeos terminaron militando en organizaciones de esta facción ideológica, y nos referimos a casos tan representativos en la época como **Claudio Orsoni** o **Pino Bolzano** entre otros muchos. La actividad proselitista de *Jeune Europe* en el último lustro de la década de los años 60, con la fundación del Partido Comunitario Europeo, nos legó una gran cantidad de publicaciones, entre las cuales destacaron *La Nation Européenne*, *La Nazione Europea* o *Europa Combattente*, cuyas portadas han servido para ilustrar las páginas interiores de nuestra obra, y que procuraron una actividad proselitista y de difusión de ideas que llegaron a imprimir semanal y mensualmente varios miles de ejemplares en Francia o en Italia. Tras agotar todas las vías posibles de alianzas y convergencias, con encuentros poco afortunados, vemos a un Thiriart que prefiere adoptar otras vías para seguir construyendo el proyecto nacional-europeo más allá de la fórmula activista y del partido político. Este es el motivo por el cual, en los siguientes años, ya en la última etapa de su vida, veremos esa transición del político activista al teórico y al ideólogo como parte de una nueva estrategia dentro del proyecto político al que consagró buena parte de su vida, y es un hecho que comienza a apreciarse desde mediados de los años 70. Durante esta época la «Europa de Brest a Bucarest» se transforma y amplía en una «Europa desde Dublín a Vladivostok». Thiriart aborda ya abiertamente la integración del espacio soviético en una Europa unida que abarca un inmenso espacio territorial, capaz de unir el Océano Atlántico y el Océano Pacífico de un extremo a otro, el «Imperio Eurosoviético». No obstante, Thiriart siempre piensa en términos geopolíticos, y considera que este proceso de integración debe llevarse a cabo desde una revisión de la ideología soviética, desde una marcada desmarxistización de su socialismo, purgado de todo dogmatismo y elementos condicionantes derivados de la teoría del Estado formulada por el marxismo-leninismo para tomar en su lugar aquella de **Thomas Hobbes**. A partir de este momento solamente hay un enemigo, el que representa el poder estadounidense y el dominio que éste ejerce sobre la Europa occidental. A partir de ese momento la URSS, bajo las premisas apuntadas por Thiriart, y desde una ideología soviética «desmarxistizada», es la que debe asumir el proyecto de integración europea. Todo este enfoque terminará conociendo su colofón final al final de la vida de Jean Thiriart, cuando éste se encuentre ya en sus último año de vida, en 1992, con una Unión Soviética ya periclitada y disuelta, con un país sumido en una crisis económica, política y social bajo el gobierno decadente de **Yeltsin**, con un poder notablemente menguado y a merced de las potencias extranjeras y las apetencias de las organizaciones financieras transnacionales. En este contexto tendrá lugar el conocido viaje de Jean Thiriart a Moscú, donde se encontrará, además de con la disidencia de Yeltsin, encabezada por el Partido Comunista dirigido por **Gennadij Ziuganov** y numerosas personalidades públicas del ámbito ruso, entre las que destacará por encima de todos el filósofo y politólogo **Aleksandr Duguin**, quien en la presente obra también reivindica la figura del belga como un contribuidor directo del [pensamiento euroasiático](https://amzn.to/3FsF3Lr). Además de medios de prensa, políticos e intelectuales rusos, nuestro autor también compartirá espacio con una pequeña delegación de la revista italiana «Orion», especializada en temática geopolítica, y representada por el padre de la geopolítica italiana, Carlo Terracciano. El encuentro no tendrá mayores consecuencias, y vendrá a significar el último acto de servicio de Jean Thiriart en su denodado esfuerzo por lograr la integración de Europa y Rusia en un poderoso bloque geopolítico capaz de hacer frente a la hegemonía estadounidense en el mundo. Terminaremos este breve y sintético escrito de presentación con un fragmento de la obra que Jean Thiriart publicó en 1965 bajo el título *¡Arriba Europa!: Una Europa unida: un imperio de 400 millones de hombres*, que nos parece de lo más adecuado para poner el punto final al presente texto: > Europa, este **MILAGRO** en la historia del hombre, este milagro que siguió al milagro griego, ha dado vida, con la prodigiosa fecundidad de su civilización irrepetible, a una cultura adoptada por el mundo entero. En la competencia surgida entre las grandes civilizaciones —occidental, india, china y japonesa— la nuestra ha aplastado a las demás. > > La **civilización** es creadora de cultura. La cultura, en cambio, jamás ha creado civilización. > > **SOLO** Europa posee la civilización; de ahí deriva su supremacía sobre los Estados Unidos y la Rusia comunista, que poseen únicamente la cultura nacida de nuestra civilización, como ha demostrado magistralmente Oswald Spengler. > > Esta cultura, separada de su civilización, está condenada a la esterilidad, la cual se manifestará primero mediante una esclerosis y, posteriormente, mediante un retorno a la barbarie. > > Políticamente dominada por Moscú o por Washington, la civilización europea se ve asfixiada y corre el riesgo de estancarse en su estado de simple cultura. Basta notar que todos los descubrimientos en el campo nuclear y astronáutico son obra de europeos. Todos buscan a los científicos europeos. > > Solo una Europa políticamente unida puede proveer los medios de poder que garantizarán las condiciones históricas indispensables para la supervivencia de esta civilización. > > Ninguna otra potencia, por otra parte, podría sustituir a Europa en su misión hacia la humanidad. --- **Artículo original**: Hipérbola Janus, [_Presentación de «Jean Thiriart, el caballero euroasiático y la Joven Europa», de Pietro Missiaggia_](https://www.hiperbolajanus.com/posts/presentacion-thiriart-missiaggia/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/presentacion-thiriart-missiaggia/), 18/Mar/2025 @ 91bea5cd:1df4451c
2025-02-04 17:15:57### Definição de ULID: Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível. #### Gerar ULID ```sql CREATE EXTENSION IF NOT EXISTS pgcrypto; CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\\000\\000\\000\\000\\000\\000'; output TEXT = ''; unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER); -- 10 entropy bytes ulid = timestamp || gen_random_bytes(10); -- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31))); -- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31))); RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ``` #### ULID TO UUID ```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF; v = regexp_split_to_array(ulid, ''); -- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]); -- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]); RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE; CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ``` #### UUID to ULID ```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN -- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31))); -- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31))); RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ``` #### Gera 11 Digitos aleatórios: YBKXG0CKTH4 ```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT; -- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars; END; $$ LANGUAGE plpgsql; ``` #### Exemplo de USO ```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL ); -- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ``` ### Fontes - https://github.com/scoville/pgsql-ulid - https://github.com/geckoboard/pgulid
@ 91bea5cd:1df4451c
2025-02-04 17:15:57### Definição de ULID: Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível. #### Gerar ULID ```sql CREATE EXTENSION IF NOT EXISTS pgcrypto; CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\\000\\000\\000\\000\\000\\000'; output TEXT = ''; unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER); -- 10 entropy bytes ulid = timestamp || gen_random_bytes(10); -- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31))); -- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31))); RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ``` #### ULID TO UUID ```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF; v = regexp_split_to_array(ulid, ''); -- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]); -- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]); RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE; CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ``` #### UUID to ULID ```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN -- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31))); -- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31))); RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ``` #### Gera 11 Digitos aleatórios: YBKXG0CKTH4 ```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT; -- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars; END; $$ LANGUAGE plpgsql; ``` #### Exemplo de USO ```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL ); -- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ``` ### Fontes - https://github.com/scoville/pgsql-ulid - https://github.com/geckoboard/pgulid @ e3ba5e1a:5e433365
2025-02-04 08:29:00President Trump has started rolling out his tariffs, something I [blogged about in November](https://www.snoyman.com/blog/2024/11/steelmanning-tariffs/). People are talking about these tariffs a lot right now, with many people (correctly) commenting on how consumers will end up with higher prices as a result of these tariffs. While that part is true, I’ve seen a lot of people taking it to the next, incorrect step: that consumers will pay the entirety of the tax. I [put up a poll on X](https://x.com/snoyberg/status/1886035800019599808) to see what people thought, and while the right answer got a lot of votes, it wasn't the winner.  For purposes of this blog post, our ultimate question will be the following: * Suppose apples currently sell for $1 each in the entire United States. * There are domestic sellers and foreign sellers of apples, all receiving the same price. * There are no taxes or tariffs on the purchase of apples. * The question is: if the US federal government puts a $0.50 import tariff per apple, what will be the change in the following: * Number of apples bought in the US * Price paid by buyers for apples in the US * Post-tax price received by domestic apple producers * Post-tax price received by foreign apple producers Before we can answer that question, we need to ask an easier, first question: before instituting the tariff, why do apples cost $1? And finally, before we dive into the details, let me provide you with the answers to the ultimate question. I recommend you try to guess these answers before reading this, and if you get it wrong, try to understand why: 1. The number of apples bought will go down 2. The buyers will pay more for each apple they buy, but not the full amount of the tariff 3. Domestic apple sellers will receive a *higher* price per apple 4. Foreign apple sellers will receive a *lower* price per apple, but not lowered by the full amount of the tariff In other words, regardless of who sends the payment to the government, both taxed parties (domestic buyers and foreign sellers) will absorb some of the costs of the tariff, while domestic sellers will benefit from the protectionism provided by tariffs and be able to sell at a higher price per unit. ## Marginal benefit All of the numbers discussed below are part of a [helper Google Sheet](https://docs.google.com/spreadsheets/d/14ZbkWpw1B9Q1UDB9Yh47DmdKQfIafVVBKbDUsSIfGZw/edit?usp=sharing) I put together for this analysis. Also, apologies about the jagged lines in the charts below, I hadn’t realized before starting on this that there are [some difficulties with creating supply and demand charts in Google Sheets](https://superuser.com/questions/1359731/how-to-create-a-supply-demand-style-chart). Let’s say I absolutely love apples, they’re my favorite food. How much would I be willing to pay for a single apple? You might say “$1, that’s the price in the supermarket,” and in many ways you’d be right. If I walk into supermarket A, see apples on sale for $50, and know that I can buy them at supermarket B for $1, I’ll almost certainly leave A and go buy at B. But that’s not what I mean. What I mean is: how high would the price of apples have to go *everywhere* so that I’d no longer be willing to buy a single apple? This is a purely personal, subjective opinion. It’s impacted by how much money I have available, other expenses I need to cover, and how much I like apples. But let’s say the number is $5. How much would I be willing to pay for another apple? Maybe another $5. But how much am I willing to pay for the 1,000th apple? 10,000th? At some point, I’ll get sick of apples, or run out of space to keep the apples, or not be able to eat, cook, and otherwise preserve all those apples before they rot. The point being: I’ll be progressively willing to spend less and less money for each apple. This form of analysis is called *marginal benefit*: how much benefit (expressed as dollars I’m willing to spend) will I receive from each apple? This is a downward sloping function: for each additional apple I buy (quantity demanded), the price I’m willing to pay goes down. This is what gives my personal *demand curve*. And if we aggregate demand curves across all market participants (meaning: everyone interested in buying apples), we end up with something like this: 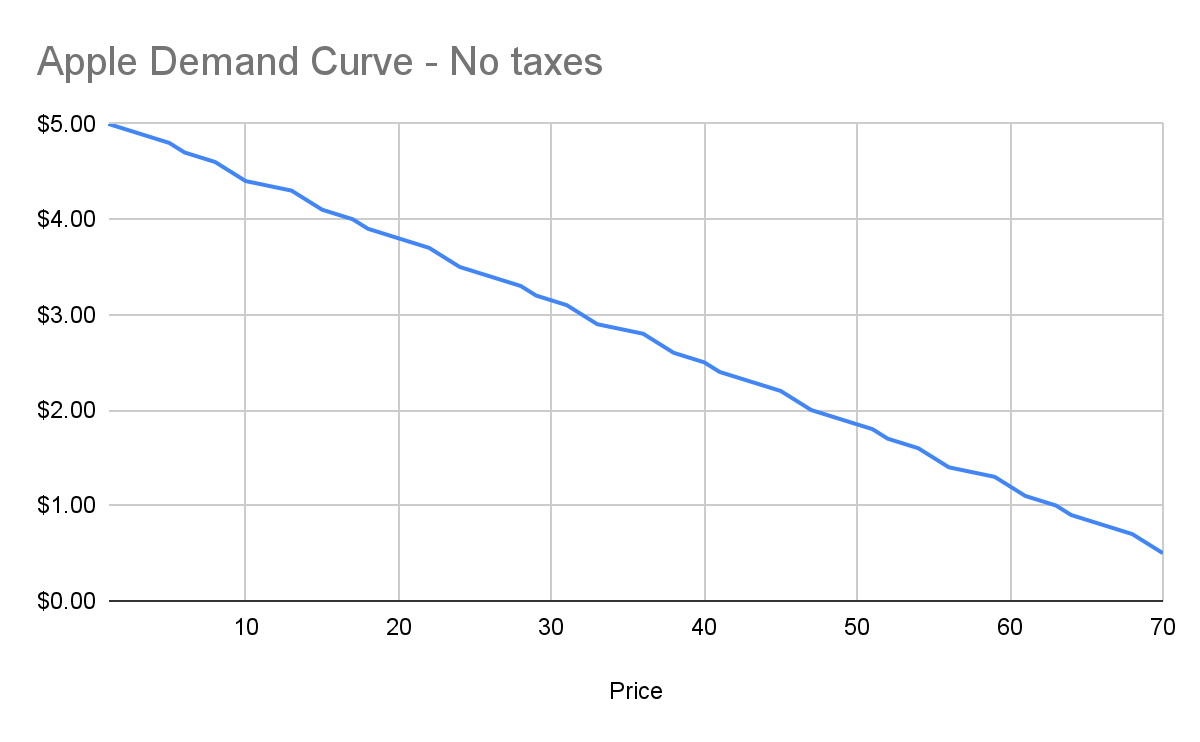 Assuming no changes in people’s behavior and other conditions in the market, this chart tells us how many apples will be purchased by our buyers at each price point between $0.50 and $5. And ceteris paribus (all else being equal), this will continue to be the demand curve for apples. ## Marginal cost Demand is half the story of economics. The other half is supply, or: how many apples will I sell at each price point? Supply curves are upward sloping: the higher the price, the more a person or company is willing and able to sell a product. Let’s understand why. Suppose I have an apple orchard. It’s a large property right next to my house. With about 2 minutes of effort, I can walk out of my house, find the nearest tree, pick 5 apples off the tree, and call it a day. 5 apples for 2 minutes of effort is pretty good, right? Yes, there was all the effort necessary to buy the land, and plant the trees, and water them… and a bunch more than I likely can’t even guess at. We’re going to ignore all of that for our analysis, because for short-term supply-and-demand movement, we can ignore these kinds of *sunk costs*. One other simplification: in reality, supply curves often start descending before ascending. This accounts for achieving efficiencies of scale after the first number of units purchased. But since both these topics are unneeded for understanding taxes, I won’t go any further. Anyway, back to my apple orchard. If someone offers me $0.50 per apple, I can do 2 minutes of effort and get $2.50 in revenue, which equates to a $75/hour wage for me. I’m more than happy to pick apples at that price\! However, let’s say someone comes to buy 10,000 apples from me instead. I no longer just walk out to my nearest tree. I’m going to need to get in my truck, drive around, spend the day in the sun, pay for gas, take a day off of my day job (let’s say it pays me $70/hour). The costs go up significantly. Let’s say it takes 5 days to harvest all those apples myself, it costs me $100 in fuel and other expenses, and I lose out on my $70/hour job for 5 days. We end up with: * Total expenditure: $100 \+ $70 \* 8 hours a day \* 5 days \== $2900 * Total revenue: $5000 (10,000 apples at $0.50 each) * Total profit: $2100 So I’m still willing to sell the apples at this price, but it’s not as attractive as before. And as the number of apples purchased goes up, my costs keep increasing. I’ll need to spend more money on fuel to travel more of my property. At some point I won’t be able to do the work myself anymore, so I’ll need to pay others to work on the farm, and they’ll be slower at picking apples than me (less familiar with the property, less direct motivation, etc.). The point being: at some point, the number of apples can go high enough that the $0.50 price point no longer makes me any money. This kind of analysis is called *marginal cost*. It refers to the additional amount of expenditure a seller has to spend in order to produce each additional unit of the good. Marginal costs go up as quantity sold goes up. And like demand curves, if you aggregate this data across all sellers, you get a supply curve like this: 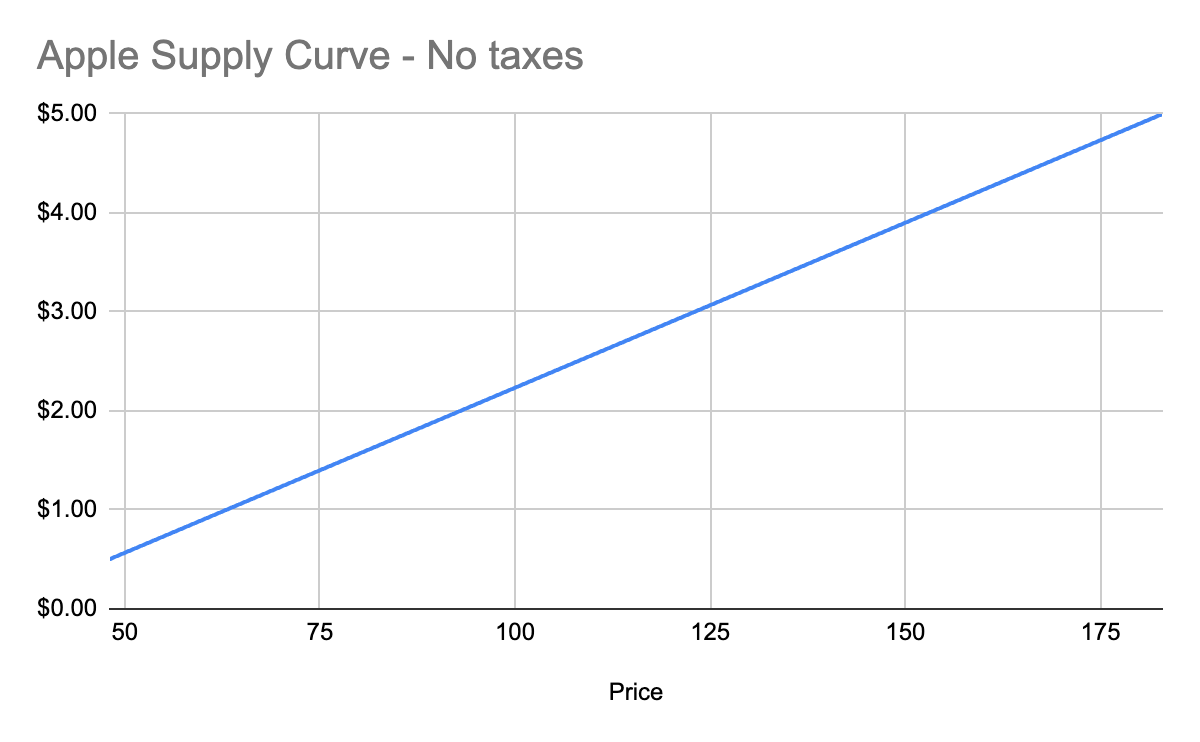 ## Equilibrium price We now know, for every price point, how many apples buyers will purchase, and how many apples sellers will sell. Now we find the equilibrium: where the supply and demand curves meet. This point represents where the marginal benefit a buyer would receive from the next buyer would be less than the cost it would take the next seller to make it. Let’s see it in a chart: 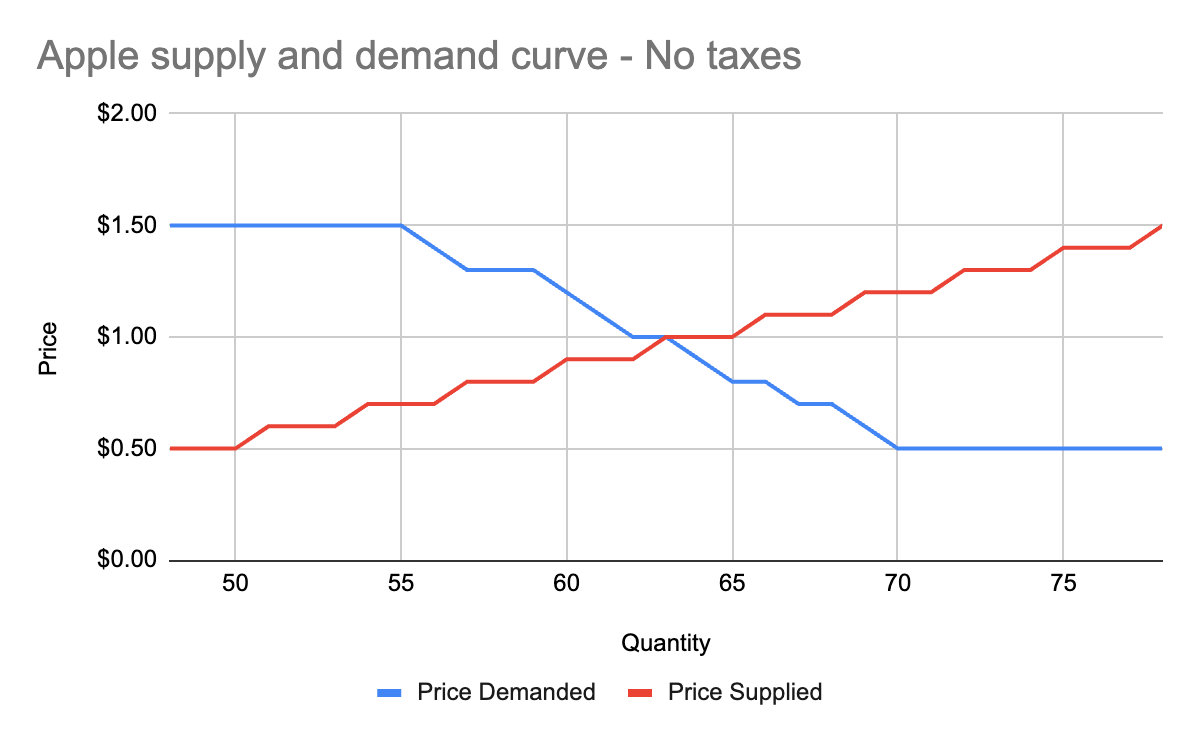 You’ll notice that these two graphs cross at the $1 price point, where 63 apples are both demanded (bought by consumers) and supplied (sold by producers). This is our equilibrium price. We also have a visualization of the *surplus* created by these trades. Everything to the left of the equilibrium point and between the supply and demand curves represents surplus: an area where someone is receiving something of more value than they give. For example: * When I bought my first apple for $1, but I was willing to spend $5, I made $4 of consumer surplus. The consumer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and above the equilibrium price point. * When a seller sells his first apple for $1, but it only cost $0.50 to produce it, the seller made $0.50 of producer surplus. The producer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and below the equilibrium price point. Another way of thinking of surplus is “every time someone got a better price than they would have been willing to take.” OK, with this in place, we now have enough information to figure out how to price in the tariff, which we’ll treat as a negative externality. ## Modeling taxes Alright, the government has now instituted a $0.50 tariff on every apple sold within the US by a foreign producer. We can generally model taxes by either increasing the marginal cost of each unit sold (shifting the supply curve up), or by decreasing the marginal benefit of each unit bought (shifting the demand curve down). In this case, since only some of the producers will pay the tax, it makes more sense to modify the supply curve. First, let’s see what happens to the foreign seller-only supply curve when you add in the tariff: 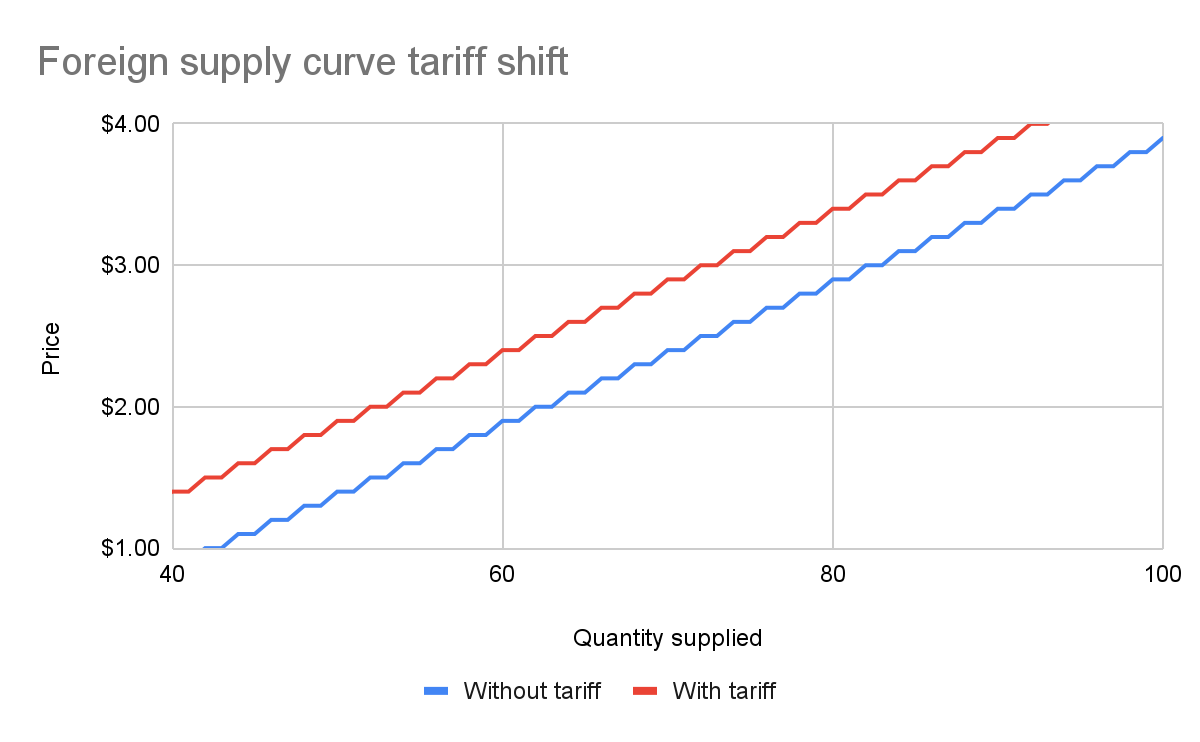 With the tariff in place, for each quantity level, the price at which the seller will sell is $0.50 higher than before the tariff. That makes sense: if I was previously willing to sell my 82nd apple for $3, I would now need to charge $3.50 for that apple to cover the cost of the tariff. We see this as the tariff “pushing up” or “pushing left” the original supply curve. We can add this new supply curve to our existing (unchanged) supply curve for domestic-only sellers, and we end up with a result like this: 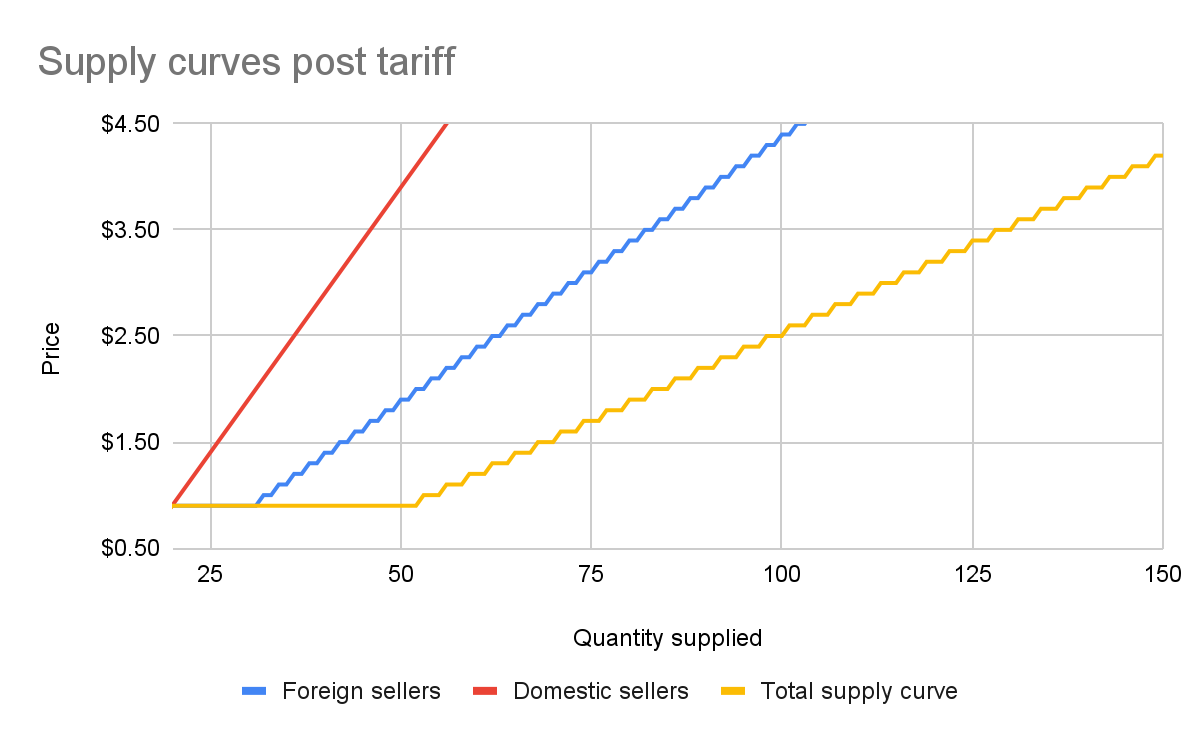 The total supply curve adds up the individual foreign and domestic supply curves. At each price point, we add up the total quantity each group would be willing to sell to determine the total quantity supplied for each price point. Once we have that cumulative supply curve defined, we can produce an updated supply-and-demand chart including the tariff: 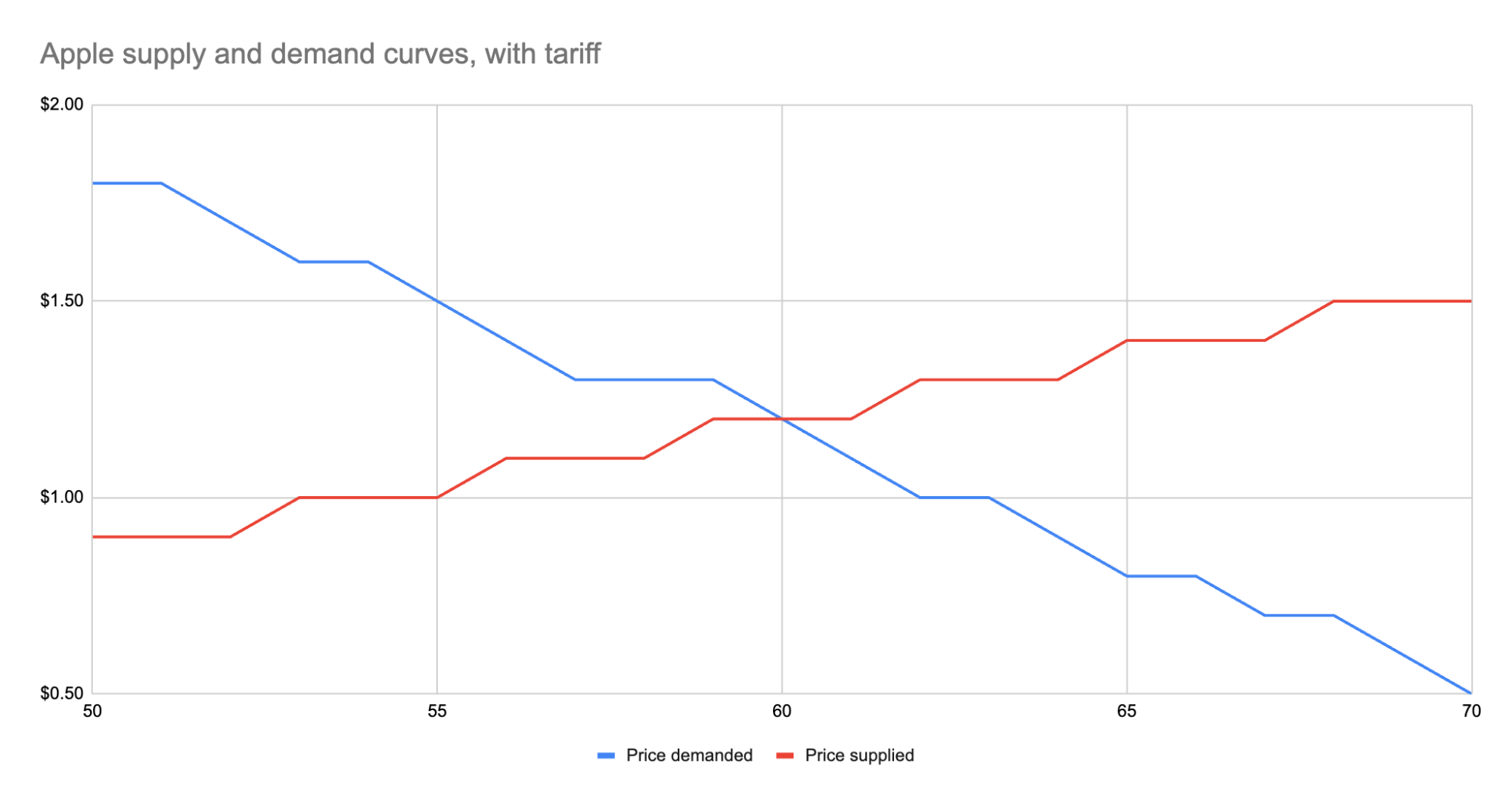 As we can see, the equilibrium has shifted: * The equilibrium price paid by consumers has risen from $1 to $1.20. * The total number of apples purchased has dropped from 63 apples to 60 apples. * Consumers therefore received 3 less apples. They spent $72 for these 60 apples, whereas previously they spent $63 for 3 more apples, a definite decrease in consumer surplus. * Foreign producers sold 36 of those apples (see the raw data in the linked Google Sheet), for a gross revenue of $43.20. However, they also need to pay the tariff to the US government, which accounts for $18, meaning they only receive $25.20 post-tariff. Previously, they sold 42 apples at $1 each with no tariff to be paid, meaning they took home $42. * Domestic producers sold the remaining 24 apples at $1.20, giving them a revenue of $28.80. Since they don’t pay the tariff, they take home all of that money. By contrast, previously, they sold 21 apples at $1, for a take-home of $21. * The government receives $0.50 for each of the 60 apples sold, or in other words receives $30 in revenue it wouldn’t have received otherwise. We could be more specific about the surpluses, and calculate the actual areas for consumer surplus, producer surplus, inefficiency from the tariff, and government revenue from the tariff. But I won’t bother, as those calculations get slightly more involved. Instead, let’s just look at the aggregate outcomes: * Consumers were unquestionably hurt. Their price paid went up by $0.20 per apple, and received less apples. * Foreign producers were also hurt. Their price received went down from the original $1 to the new post-tariff price of $1.20, minus the $0.50 tariff. In other words: foreign producers only receive $0.70 per apple now. This hurt can be mitigated by shifting sales to other countries without a tariff, but the pain will exist regardless. * Domestic producers scored. They can sell less apples and make more revenue doing it. * And the government walked away with an extra $30. Hopefully you now see the answer to the original questions. Importantly, while the government imposed a $0.50 tariff, neither side fully absorbed that cost. Consumers paid a bit more, foreign producers received a bit less. The exact details of how that tariff was split across the groups is mediated by the relevant supply and demand curves of each group. If you want to learn more about this, the relevant search term is “price elasticity,” or how much a group’s quantity supplied or demanded will change based on changes in the price. ## Other taxes Most taxes are some kind of a tax on trade. Tariffs on apples is an obvious one. But the same applies to income tax (taxing the worker for the trade of labor for money) or payroll tax (same thing, just taxing the employer instead). Interestingly, you can use the same model for analyzing things like tax incentives. For example, if the government decided to subsidize domestic apple production by giving the domestic producers a $0.50 bonus for each apple they sell, we would end up with a similar kind of analysis, except instead of the foreign supply curve shifting up, we’d see the domestic supply curve shifting down. And generally speaking, this is what you’ll *always* see with government involvement in the economy. It will result in disrupting an existing equilibrium, letting the market readjust to a new equilibrium, and incentivization of some behavior, causing some people to benefit and others to lose out. We saw with the apple tariff, domestic producers and the government benefited while others lost. You can see the reverse though with tax incentives. If I give a tax incentive of providing a deduction (not paying income tax) for preschool, we would end up with: * Government needs to make up the difference in tax revenue, either by raising taxes on others or printing more money (leading to inflation). Either way, those paying the tax or those holding government debased currency will pay a price. * Those people who don’t use the preschool deduction will receive no benefit, so they simply pay a cost. * Those who do use the preschool deduction will end up paying less on tax+preschool than they would have otherwise. This analysis is fully amoral. It’s not saying whether providing subsidized preschool is a good thing or not, it simply tells you where the costs will be felt, and points out that such government interference in free economic choice does result in inefficiencies in the system. Once you have that knowledge, you’re more well educated on making a decision about whether the costs of government intervention are worth the benefits.
@ e3ba5e1a:5e433365
2025-02-04 08:29:00President Trump has started rolling out his tariffs, something I [blogged about in November](https://www.snoyman.com/blog/2024/11/steelmanning-tariffs/). People are talking about these tariffs a lot right now, with many people (correctly) commenting on how consumers will end up with higher prices as a result of these tariffs. While that part is true, I’ve seen a lot of people taking it to the next, incorrect step: that consumers will pay the entirety of the tax. I [put up a poll on X](https://x.com/snoyberg/status/1886035800019599808) to see what people thought, and while the right answer got a lot of votes, it wasn't the winner.  For purposes of this blog post, our ultimate question will be the following: * Suppose apples currently sell for $1 each in the entire United States. * There are domestic sellers and foreign sellers of apples, all receiving the same price. * There are no taxes or tariffs on the purchase of apples. * The question is: if the US federal government puts a $0.50 import tariff per apple, what will be the change in the following: * Number of apples bought in the US * Price paid by buyers for apples in the US * Post-tax price received by domestic apple producers * Post-tax price received by foreign apple producers Before we can answer that question, we need to ask an easier, first question: before instituting the tariff, why do apples cost $1? And finally, before we dive into the details, let me provide you with the answers to the ultimate question. I recommend you try to guess these answers before reading this, and if you get it wrong, try to understand why: 1. The number of apples bought will go down 2. The buyers will pay more for each apple they buy, but not the full amount of the tariff 3. Domestic apple sellers will receive a *higher* price per apple 4. Foreign apple sellers will receive a *lower* price per apple, but not lowered by the full amount of the tariff In other words, regardless of who sends the payment to the government, both taxed parties (domestic buyers and foreign sellers) will absorb some of the costs of the tariff, while domestic sellers will benefit from the protectionism provided by tariffs and be able to sell at a higher price per unit. ## Marginal benefit All of the numbers discussed below are part of a [helper Google Sheet](https://docs.google.com/spreadsheets/d/14ZbkWpw1B9Q1UDB9Yh47DmdKQfIafVVBKbDUsSIfGZw/edit?usp=sharing) I put together for this analysis. Also, apologies about the jagged lines in the charts below, I hadn’t realized before starting on this that there are [some difficulties with creating supply and demand charts in Google Sheets](https://superuser.com/questions/1359731/how-to-create-a-supply-demand-style-chart). Let’s say I absolutely love apples, they’re my favorite food. How much would I be willing to pay for a single apple? You might say “$1, that’s the price in the supermarket,” and in many ways you’d be right. If I walk into supermarket A, see apples on sale for $50, and know that I can buy them at supermarket B for $1, I’ll almost certainly leave A and go buy at B. But that’s not what I mean. What I mean is: how high would the price of apples have to go *everywhere* so that I’d no longer be willing to buy a single apple? This is a purely personal, subjective opinion. It’s impacted by how much money I have available, other expenses I need to cover, and how much I like apples. But let’s say the number is $5. How much would I be willing to pay for another apple? Maybe another $5. But how much am I willing to pay for the 1,000th apple? 10,000th? At some point, I’ll get sick of apples, or run out of space to keep the apples, or not be able to eat, cook, and otherwise preserve all those apples before they rot. The point being: I’ll be progressively willing to spend less and less money for each apple. This form of analysis is called *marginal benefit*: how much benefit (expressed as dollars I’m willing to spend) will I receive from each apple? This is a downward sloping function: for each additional apple I buy (quantity demanded), the price I’m willing to pay goes down. This is what gives my personal *demand curve*. And if we aggregate demand curves across all market participants (meaning: everyone interested in buying apples), we end up with something like this: 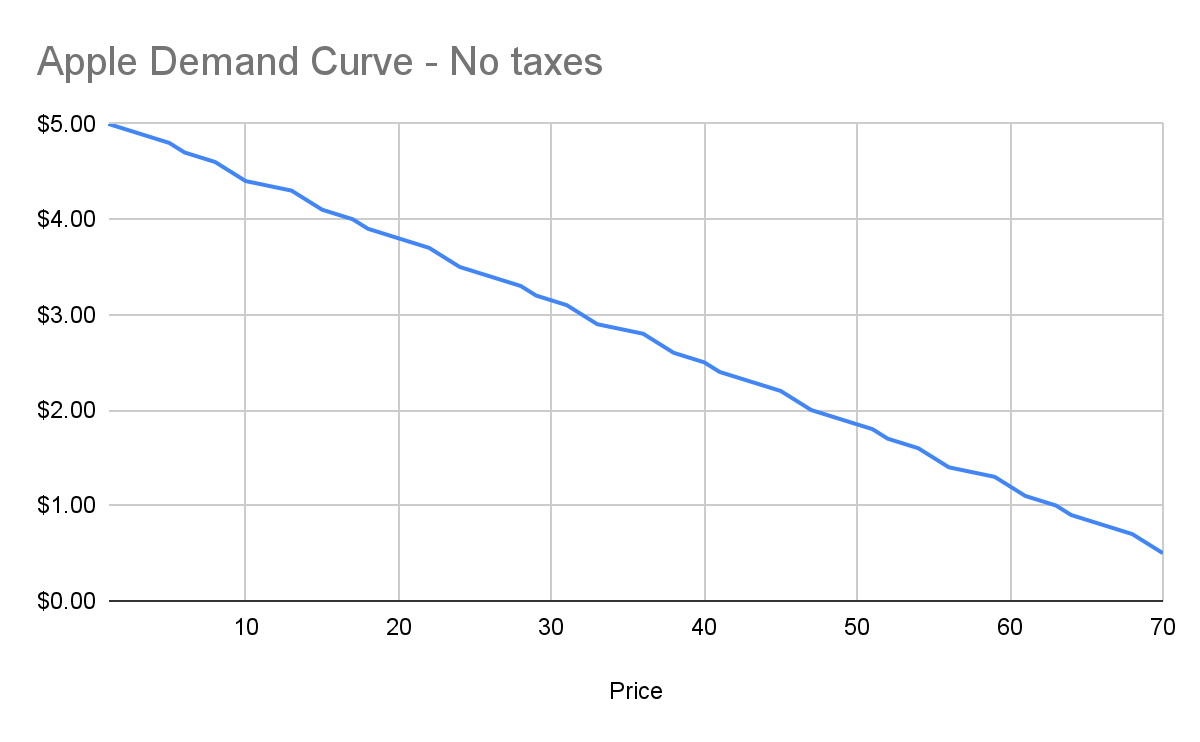 Assuming no changes in people’s behavior and other conditions in the market, this chart tells us how many apples will be purchased by our buyers at each price point between $0.50 and $5. And ceteris paribus (all else being equal), this will continue to be the demand curve for apples. ## Marginal cost Demand is half the story of economics. The other half is supply, or: how many apples will I sell at each price point? Supply curves are upward sloping: the higher the price, the more a person or company is willing and able to sell a product. Let’s understand why. Suppose I have an apple orchard. It’s a large property right next to my house. With about 2 minutes of effort, I can walk out of my house, find the nearest tree, pick 5 apples off the tree, and call it a day. 5 apples for 2 minutes of effort is pretty good, right? Yes, there was all the effort necessary to buy the land, and plant the trees, and water them… and a bunch more than I likely can’t even guess at. We’re going to ignore all of that for our analysis, because for short-term supply-and-demand movement, we can ignore these kinds of *sunk costs*. One other simplification: in reality, supply curves often start descending before ascending. This accounts for achieving efficiencies of scale after the first number of units purchased. But since both these topics are unneeded for understanding taxes, I won’t go any further. Anyway, back to my apple orchard. If someone offers me $0.50 per apple, I can do 2 minutes of effort and get $2.50 in revenue, which equates to a $75/hour wage for me. I’m more than happy to pick apples at that price\! However, let’s say someone comes to buy 10,000 apples from me instead. I no longer just walk out to my nearest tree. I’m going to need to get in my truck, drive around, spend the day in the sun, pay for gas, take a day off of my day job (let’s say it pays me $70/hour). The costs go up significantly. Let’s say it takes 5 days to harvest all those apples myself, it costs me $100 in fuel and other expenses, and I lose out on my $70/hour job for 5 days. We end up with: * Total expenditure: $100 \+ $70 \* 8 hours a day \* 5 days \== $2900 * Total revenue: $5000 (10,000 apples at $0.50 each) * Total profit: $2100 So I’m still willing to sell the apples at this price, but it’s not as attractive as before. And as the number of apples purchased goes up, my costs keep increasing. I’ll need to spend more money on fuel to travel more of my property. At some point I won’t be able to do the work myself anymore, so I’ll need to pay others to work on the farm, and they’ll be slower at picking apples than me (less familiar with the property, less direct motivation, etc.). The point being: at some point, the number of apples can go high enough that the $0.50 price point no longer makes me any money. This kind of analysis is called *marginal cost*. It refers to the additional amount of expenditure a seller has to spend in order to produce each additional unit of the good. Marginal costs go up as quantity sold goes up. And like demand curves, if you aggregate this data across all sellers, you get a supply curve like this: 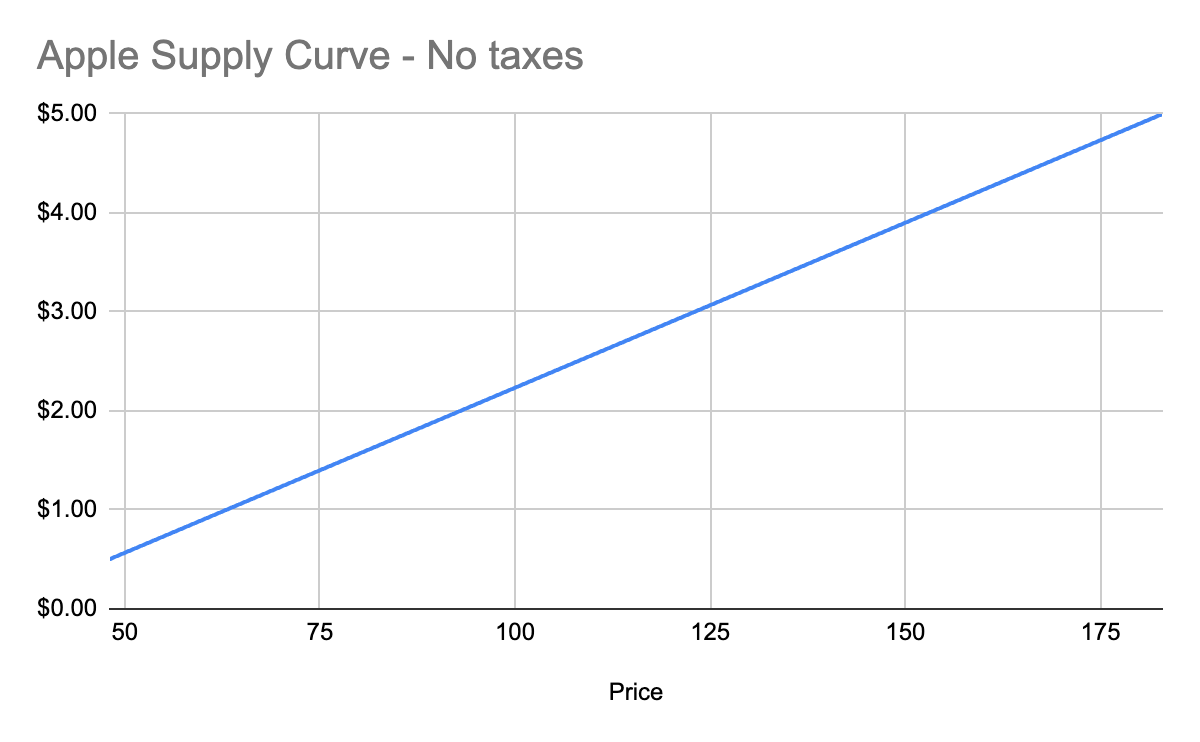 ## Equilibrium price We now know, for every price point, how many apples buyers will purchase, and how many apples sellers will sell. Now we find the equilibrium: where the supply and demand curves meet. This point represents where the marginal benefit a buyer would receive from the next buyer would be less than the cost it would take the next seller to make it. Let’s see it in a chart: 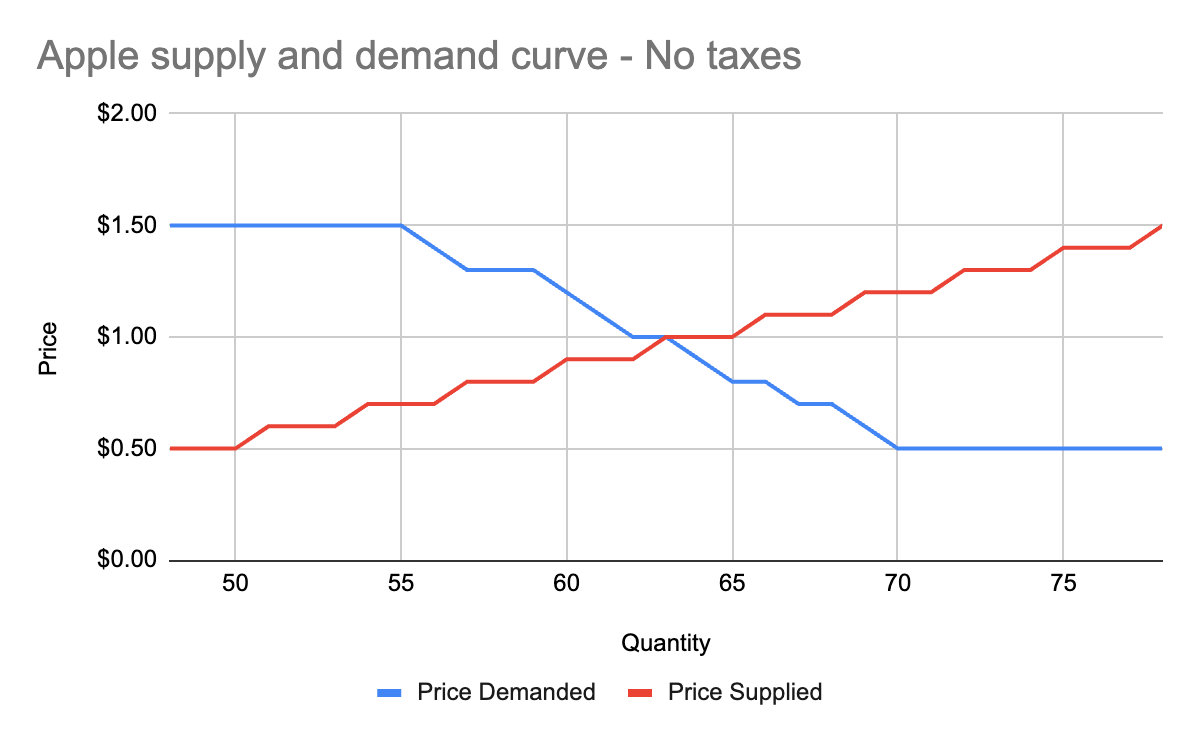 You’ll notice that these two graphs cross at the $1 price point, where 63 apples are both demanded (bought by consumers) and supplied (sold by producers). This is our equilibrium price. We also have a visualization of the *surplus* created by these trades. Everything to the left of the equilibrium point and between the supply and demand curves represents surplus: an area where someone is receiving something of more value than they give. For example: * When I bought my first apple for $1, but I was willing to spend $5, I made $4 of consumer surplus. The consumer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and above the equilibrium price point. * When a seller sells his first apple for $1, but it only cost $0.50 to produce it, the seller made $0.50 of producer surplus. The producer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and below the equilibrium price point. Another way of thinking of surplus is “every time someone got a better price than they would have been willing to take.” OK, with this in place, we now have enough information to figure out how to price in the tariff, which we’ll treat as a negative externality. ## Modeling taxes Alright, the government has now instituted a $0.50 tariff on every apple sold within the US by a foreign producer. We can generally model taxes by either increasing the marginal cost of each unit sold (shifting the supply curve up), or by decreasing the marginal benefit of each unit bought (shifting the demand curve down). In this case, since only some of the producers will pay the tax, it makes more sense to modify the supply curve. First, let’s see what happens to the foreign seller-only supply curve when you add in the tariff: 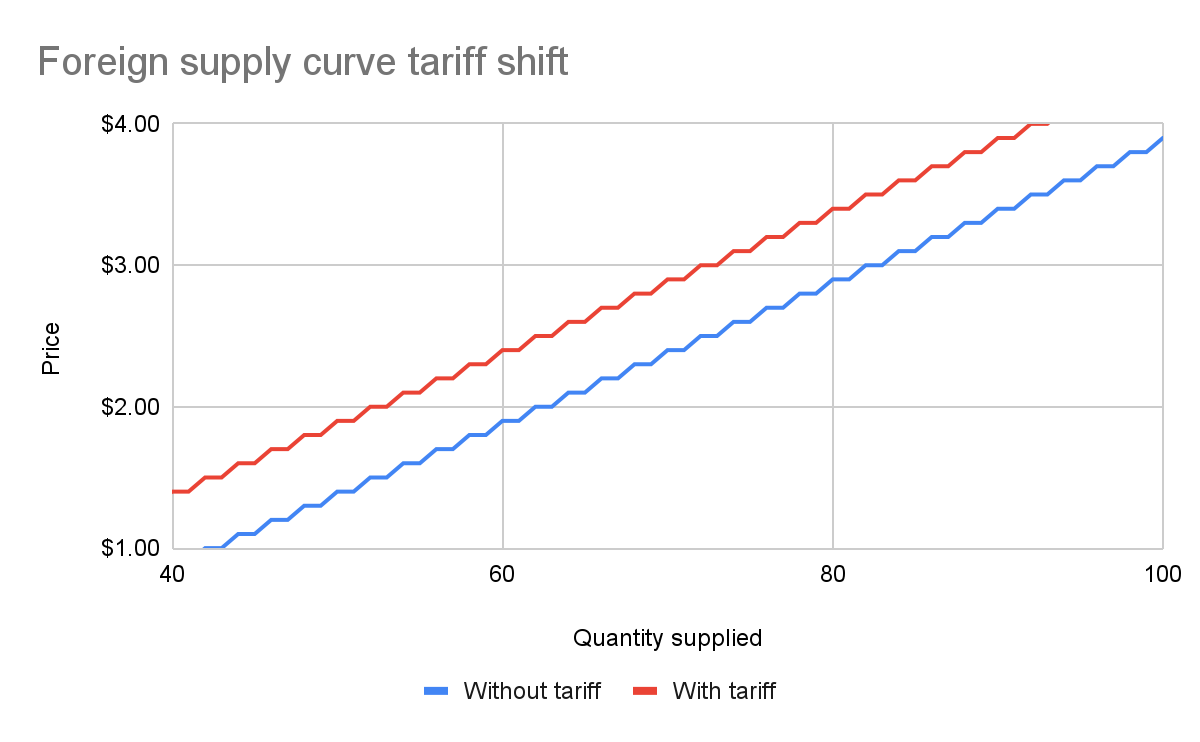 With the tariff in place, for each quantity level, the price at which the seller will sell is $0.50 higher than before the tariff. That makes sense: if I was previously willing to sell my 82nd apple for $3, I would now need to charge $3.50 for that apple to cover the cost of the tariff. We see this as the tariff “pushing up” or “pushing left” the original supply curve. We can add this new supply curve to our existing (unchanged) supply curve for domestic-only sellers, and we end up with a result like this: 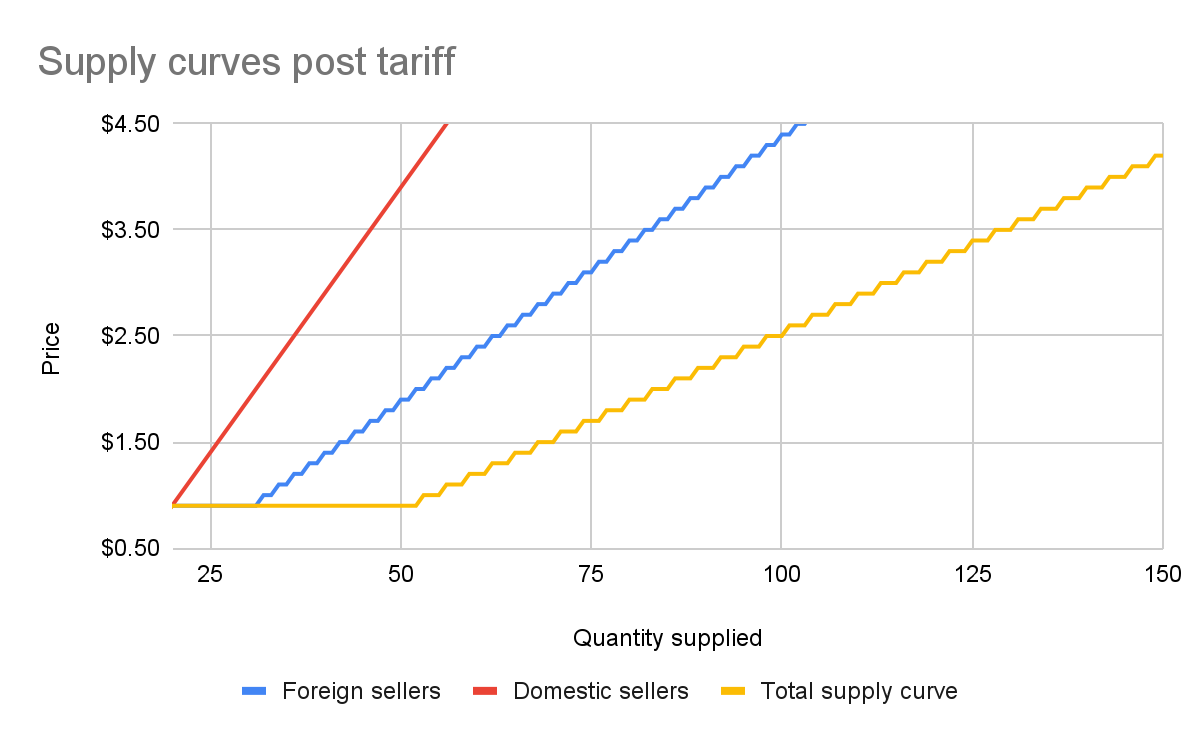 The total supply curve adds up the individual foreign and domestic supply curves. At each price point, we add up the total quantity each group would be willing to sell to determine the total quantity supplied for each price point. Once we have that cumulative supply curve defined, we can produce an updated supply-and-demand chart including the tariff: 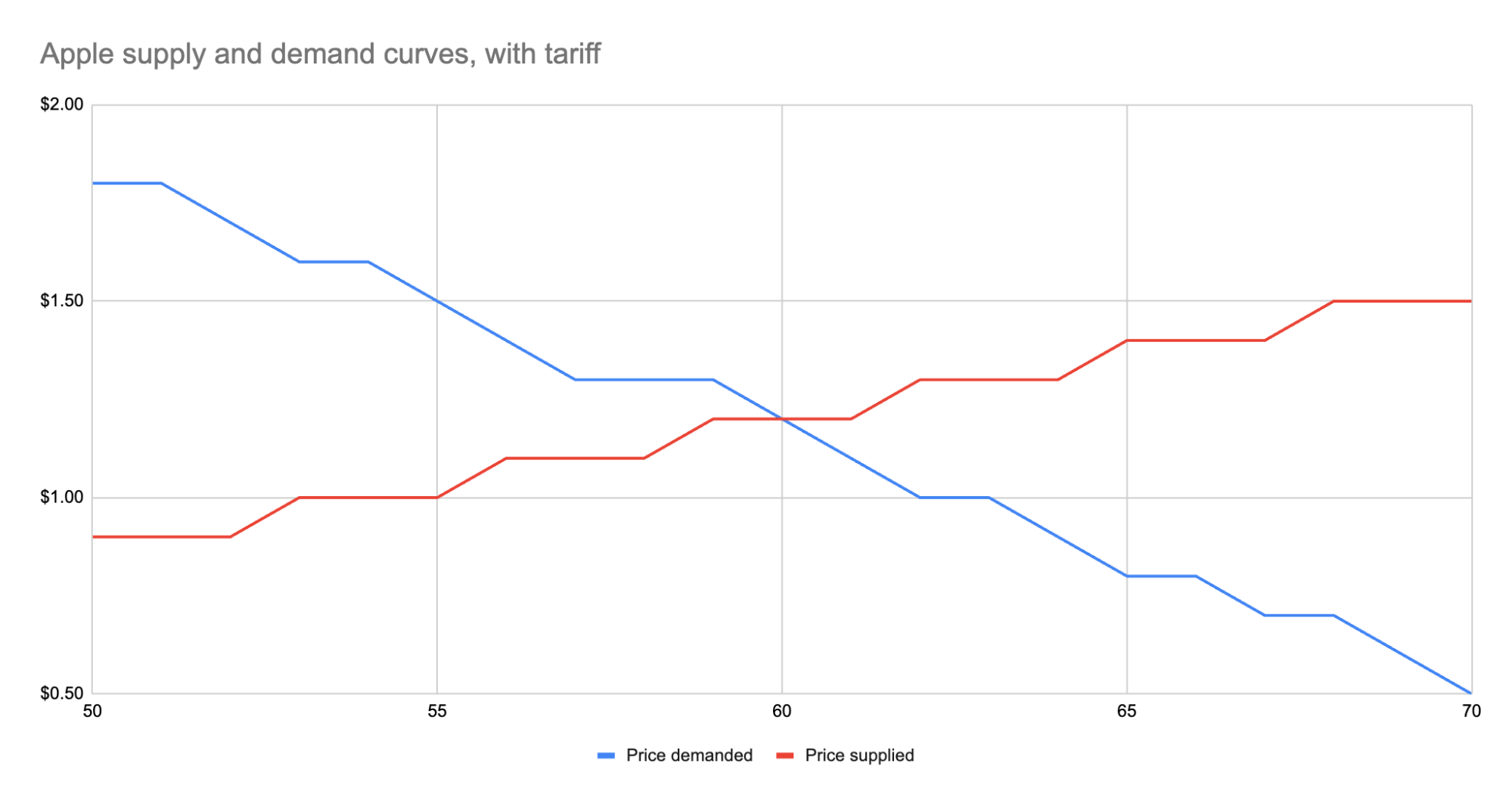 As we can see, the equilibrium has shifted: * The equilibrium price paid by consumers has risen from $1 to $1.20. * The total number of apples purchased has dropped from 63 apples to 60 apples. * Consumers therefore received 3 less apples. They spent $72 for these 60 apples, whereas previously they spent $63 for 3 more apples, a definite decrease in consumer surplus. * Foreign producers sold 36 of those apples (see the raw data in the linked Google Sheet), for a gross revenue of $43.20. However, they also need to pay the tariff to the US government, which accounts for $18, meaning they only receive $25.20 post-tariff. Previously, they sold 42 apples at $1 each with no tariff to be paid, meaning they took home $42. * Domestic producers sold the remaining 24 apples at $1.20, giving them a revenue of $28.80. Since they don’t pay the tariff, they take home all of that money. By contrast, previously, they sold 21 apples at $1, for a take-home of $21. * The government receives $0.50 for each of the 60 apples sold, or in other words receives $30 in revenue it wouldn’t have received otherwise. We could be more specific about the surpluses, and calculate the actual areas for consumer surplus, producer surplus, inefficiency from the tariff, and government revenue from the tariff. But I won’t bother, as those calculations get slightly more involved. Instead, let’s just look at the aggregate outcomes: * Consumers were unquestionably hurt. Their price paid went up by $0.20 per apple, and received less apples. * Foreign producers were also hurt. Their price received went down from the original $1 to the new post-tariff price of $1.20, minus the $0.50 tariff. In other words: foreign producers only receive $0.70 per apple now. This hurt can be mitigated by shifting sales to other countries without a tariff, but the pain will exist regardless. * Domestic producers scored. They can sell less apples and make more revenue doing it. * And the government walked away with an extra $30. Hopefully you now see the answer to the original questions. Importantly, while the government imposed a $0.50 tariff, neither side fully absorbed that cost. Consumers paid a bit more, foreign producers received a bit less. The exact details of how that tariff was split across the groups is mediated by the relevant supply and demand curves of each group. If you want to learn more about this, the relevant search term is “price elasticity,” or how much a group’s quantity supplied or demanded will change based on changes in the price. ## Other taxes Most taxes are some kind of a tax on trade. Tariffs on apples is an obvious one. But the same applies to income tax (taxing the worker for the trade of labor for money) or payroll tax (same thing, just taxing the employer instead). Interestingly, you can use the same model for analyzing things like tax incentives. For example, if the government decided to subsidize domestic apple production by giving the domestic producers a $0.50 bonus for each apple they sell, we would end up with a similar kind of analysis, except instead of the foreign supply curve shifting up, we’d see the domestic supply curve shifting down. And generally speaking, this is what you’ll *always* see with government involvement in the economy. It will result in disrupting an existing equilibrium, letting the market readjust to a new equilibrium, and incentivization of some behavior, causing some people to benefit and others to lose out. We saw with the apple tariff, domestic producers and the government benefited while others lost. You can see the reverse though with tax incentives. If I give a tax incentive of providing a deduction (not paying income tax) for preschool, we would end up with: * Government needs to make up the difference in tax revenue, either by raising taxes on others or printing more money (leading to inflation). Either way, those paying the tax or those holding government debased currency will pay a price. * Those people who don’t use the preschool deduction will receive no benefit, so they simply pay a cost. * Those who do use the preschool deduction will end up paying less on tax+preschool than they would have otherwise. This analysis is fully amoral. It’s not saying whether providing subsidized preschool is a good thing or not, it simply tells you where the costs will be felt, and points out that such government interference in free economic choice does result in inefficiencies in the system. Once you have that knowledge, you’re more well educated on making a decision about whether the costs of government intervention are worth the benefits. @ 9e69e420:d12360c2
2025-02-01 11:16:04 Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.  CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language. One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
@ 9e69e420:d12360c2
2025-02-01 11:16:04 Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.  CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language. One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse. @ 97c70a44:ad98e322
2025-01-30 17:15:37There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test. In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go. # It uses nostr The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol. Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key. In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along. In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim. # It leverages nostr Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app". This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back. Some examples might include: - Using nostr signers to encrypt or sign data, and then store that data on a proprietary server. - Using nostr relays as a kind of low-code backend, but using proprietary event payloads. - Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you. An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem. In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering. # It complements nostr Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role. One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense. Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)? A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs. To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen. # It embodies nostr Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate. This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product? To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the *protocol*, while apps that benefit nostr exclusively via network effect are integrated into nostr the *network*. An app that does both things is working in symbiosis with nostr as a whole. An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem: - In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors. - In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for. Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency _as nostr users_. If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states: > Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions. These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers. _As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria._ Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type". To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well, - There is a [spec](https://github.com/nostr-protocol/nips/pull/1190) for forms and responses, which means that... - Multiple clients can implement the same data format, allowing for credible exit and user choice, even of... - Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does... - Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to... - Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost". Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr. # It supports nostr Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually). This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content? In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together. A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own. So while I might hesitate to call many of these things "apps", they are certainly "nostr". # Appendix: it smells like a NINO So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr. You app might be a NINO if: - There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind) - There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository) - Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr - Your NIP relies on trusted third (or first) parties - There's only one implementation of your NIP (yours) - Your core value proposition doesn't depend on relays, events, or nostr identities - One or more relay urls are hard-coded into the source code - Your app depends on a specific relay implementation to work (*ahem*, relay29) - You don't validate event signatures - You don't publish events to relays you don't control - You don't read events from relays you don't control - You use legacy web services to solve problems, rather than nostr-native solutions - You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app - You don't use NIP 89 to discover clients and services - You haven't published a NIP 89 listing for your app - You don't leverage your users' web of trust for filtering out spam - You don't respect your users' mute lists - You try to "own" your users' data Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product. If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation: - Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine. - Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc. - Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats. - Think your idea is a good one? Talk to other devs or open a PR to the [nips repo](https://github.com/nostr-protocol/nips). No one can adopt your NIP if they don't know about it. - Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated. - Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask! I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV.
@ 97c70a44:ad98e322
2025-01-30 17:15:37There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test. In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go. # It uses nostr The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol. Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key. In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along. In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim. # It leverages nostr Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app". This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back. Some examples might include: - Using nostr signers to encrypt or sign data, and then store that data on a proprietary server. - Using nostr relays as a kind of low-code backend, but using proprietary event payloads. - Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you. An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem. In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering. # It complements nostr Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role. One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense. Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)? A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs. To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen. # It embodies nostr Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate. This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product? To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the *protocol*, while apps that benefit nostr exclusively via network effect are integrated into nostr the *network*. An app that does both things is working in symbiosis with nostr as a whole. An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem: - In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors. - In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for. Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency _as nostr users_. If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states: > Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions. These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers. _As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria._ Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type". To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well, - There is a [spec](https://github.com/nostr-protocol/nips/pull/1190) for forms and responses, which means that... - Multiple clients can implement the same data format, allowing for credible exit and user choice, even of... - Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does... - Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to... - Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost". Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr. # It supports nostr Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually). This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content? In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together. A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own. So while I might hesitate to call many of these things "apps", they are certainly "nostr". # Appendix: it smells like a NINO So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr. You app might be a NINO if: - There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind) - There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository) - Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr - Your NIP relies on trusted third (or first) parties - There's only one implementation of your NIP (yours) - Your core value proposition doesn't depend on relays, events, or nostr identities - One or more relay urls are hard-coded into the source code - Your app depends on a specific relay implementation to work (*ahem*, relay29) - You don't validate event signatures - You don't publish events to relays you don't control - You don't read events from relays you don't control - You use legacy web services to solve problems, rather than nostr-native solutions - You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app - You don't use NIP 89 to discover clients and services - You haven't published a NIP 89 listing for your app - You don't leverage your users' web of trust for filtering out spam - You don't respect your users' mute lists - You try to "own" your users' data Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product. If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation: - Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine. - Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc. - Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats. - Think your idea is a good one? Talk to other devs or open a PR to the [nips repo](https://github.com/nostr-protocol/nips). No one can adopt your NIP if they don't know about it. - Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated. - Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask! I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV. @ 9e69e420:d12360c2
2025-01-30 12:23:04Tech stocks have taken a hit globally after China's DeepSeek launched a competitive AI chatbot at a much lower cost than US counterparts. This has stirred market fears of a $1.2 trillion loss across tech companies when trading opens in New York. DeepSeek’s chatbot quickly topped download charts and surprised experts with its capabilities, developed for only $5.6 million. The Nasdaq dropped over 3% in premarket trading, with major firms like Nvidia falling more than 10%. SoftBank also saw losses shortly after investing in a significant US AI venture. Venture capitalist Marc Andreessen called it “AI’s Sputnik moment,” highlighting its potential impact on the industry. ![] (https://www.telegraph.co.uk/content/dam/business/2025/01/27/TELEMMGLPICT000409807198_17379939060750_trans_NvBQzQNjv4BqgsaO8O78rhmZrDxTlQBjdGLvJF5WfpqnBZShRL_tOZw.jpeg)
@ 9e69e420:d12360c2
2025-01-30 12:23:04Tech stocks have taken a hit globally after China's DeepSeek launched a competitive AI chatbot at a much lower cost than US counterparts. This has stirred market fears of a $1.2 trillion loss across tech companies when trading opens in New York. DeepSeek’s chatbot quickly topped download charts and surprised experts with its capabilities, developed for only $5.6 million. The Nasdaq dropped over 3% in premarket trading, with major firms like Nvidia falling more than 10%. SoftBank also saw losses shortly after investing in a significant US AI venture. Venture capitalist Marc Andreessen called it “AI’s Sputnik moment,” highlighting its potential impact on the industry. ![] (https://www.telegraph.co.uk/content/dam/business/2025/01/27/TELEMMGLPICT000409807198_17379939060750_trans_NvBQzQNjv4BqgsaO8O78rhmZrDxTlQBjdGLvJF5WfpqnBZShRL_tOZw.jpeg) @ bcbb3e40:a494e501
2025-03-31 15:23:12|[](https://www.hiperbolajanus.com/libros/esoterismo-berard-fata/)| |:-:| |[BÉRARD, Bruno y LA FATA, Aldo; _¿Qué es el esoterismo?: Entre verdades y falsificacioines_; Hipérbola Janus, 2025](https://hiperbolajanus.com/libros/esoterismo-berard-fata/)| Nos complace presentar al lector en lengua española una novedad de primer orden, y sobre un tema que viene siendo objeto de interés por parte de nuestra línea editorial, como es el esoterismo, que hemos abordado recientemente a través de un nuevo recopilatorio de la obra evoliana en [*Ensayos filosóficos, esotéricos y religiosos 1925-1931*](https://hiperbolajanus.com/posts/presentacion-ensayos-filosoficos-evola/), donde hemos tratado de rescatar los textos de las primeras etapas en la formulación del pensamiento del Maestro Romano. No obstante, no es la primera aventura que hemos emprendido en este terreno, siempre complejo y acompañado de la etiqueta, popular y quizás vulgarizada, de lo «misterioso» y lo «oculto», aunque no somos nada sospechosos en ese sentido por banalizar o tratar de ofrecer un enfoque puramente literario del asunto, y ni mucho menos de simpatizar con aquellas vías que entroncan con el *New age*, donde las mixtificaciones y la voluntad de convertir el fenómeno esotérico en un producto de consumo más, como demanda el mercado, para satisfacer demandas materiales o simples modas de una masa sobresocializada son norma habitual. Podríamos citar multitud de obras que están presentes en nuestro catálogo, como son [*El pensamiento esotérico de Leonardo*](https://hiperbolajanus.com/posts/presentacion-pensamiento-esoterico-leonardo-paul-vulliaud/), de **Paul Vulliaud**, [*El mundo mágico de los héroes*](https://hiperbolajanus.com/posts/mundo-magico-heroes-cesare-riviera/), de **Cesare della Riviera**, una joya del esoterismo italiano del siglo XVII, en [*El maestro de la tradición perenne*](https://hiperbolajanus.com/posts/rene-guenon-maestro-tradicion-perenne/), de **René Guénon**, o en el ensayo de **Gianluca Marletta** [*OVNIS y alienígenas. Origen, historia y prodigio de una pseudorreligión*](https://hiperbolajanus.com/posts/ovnis-alienigenas-gianluca-marletta/), un ensayo de notable originalidad donde se abordan aspectos esotéricos, aunque sea de un modo más tangencial. También en la literatura, con la obra del gran mitólogo y literato **Boris Nad**, [*Una historia de Agartha*](https://hiperbolajanus.com/posts/historia-agartha-boris-nad/) y [*La muerte púrpura*](https://hiperbolajanus.com/posts/gustav-meyrink/) de **Gustav Meyrink** encontramos nuevas referencias al ámbito esotérico. De modo que podemos concluir en que el esoterismo forma parte esencial de nuestras publicaciones e intereses como editores, y contribuimos activamente a su difusión. |[](https://www.hiperbolajanus.com/libros/ensayos-filosoficos-esotericos-religiosos-evola/)| |:-:| |[EVOLA, Julius; _Ensayos filosóficos, esotéricos y religiosos: 1925-1931_, Hiperbola Janus, 2024](https://www.hiperbolajanus.com/libros/ensayos-filosoficos-esotericos-religiosos-evola/)| # Una obra original Por eso la presente obra, la que nos disponemos a presentar, cuyo título es *¿Qué es el esoterismo?: Entre verdades y falsificaciones*, de **Bruno Bérard** y **Aldo La Fata**, viene a ser una obra muy necesaria y clarificadora en la comprensión del esoterismo en todas sus dimensiones, en la complejidad de sus particulares, y en sus múltiples manifestaciones. Quizás en el mundo de habla hispana el esoterismo es un fenómeno que no ha obtenido su merecida atención, y nuestros autores en este ámbito, como es el caso de un **Ramón Llull** entre otros, no sean objeto de la atención que merece, y las actividades esotéricas, a nivel de asociaciones, comunidades u otras formas de organización, tampoco sean especialmente conocidas, ni cuenten con una actividad reconocida. Es posible, como señala La Fata, que haya ciertas reticencias dentro del mundo católico, acostumbrado a la ortodoxia y la guía espiritual de la Iglesia, y que cualquier tipo de «desviación» hacia formas más individuales y «libres» de vivir ciertas formas iniciáticas, mucho más sutiles, provoquen el rechazo y la incomprensión general. No obstante, como también se encargan de aclarar nuestros autores, el esoterismo comprende una dimensión diferenciada, implica un esfuerzo que no todos están dispuestos a acometer, y finalmente, no es tampoco un camino de felicidad y de frutos seguros, implica una transformación interior y la asunción de unas prácticas y procedimientos que no son aptos para cualquiera. Digamos que el esoterismo es un camino, una vía, que a diferencia de las «religiones populares», exotéricas, supone un arduo camino que viene marcado por un principio vertical y aristocrático de la existencia, o al menos así queremos verlo nosotros. El incremento de la capacidad de discernimiento, aunar lo visible con lo invisible, y ser capaz de superar límites vedados al común, no por simple vanidad ni por «crecimiento personal», tal y como se concibe en las aburguesadas y decadentes sociedades actuales, sino como parte de un proceso de aprendizaje, de autoconocimiento y de liberación. No nos cabe duda alguna de la necesidad de restaurar los antiguos vínculos con lo Alto, las vías que quedaron cerradas y que nos han limitado progresivamente al exclusivo y estrecho ámbito de la materialidad. |[](https://www.hiperbolajanus.com/libros/mundo-magico-heroes-cesare-riviera/)| |:-:| |[RIVIERA, Cesare della; _El mundo mágico de los héroes_; Hipérbola Janus, 2022](https://www.hiperbolajanus.com/libros/mundo-magico-heroes-cesare-riviera/)| La obra emplea el recurso de la entrevista/diálogo, que aporta frescura y fluidez al texto «simplificando», o más bien haciendo más accesibles y comprensibles elementos relacionados con el esoterismo, que de otro modo resultarían excesivamente complejos para una parte del público lector poco familiarizado con la materia. Este dinamismo se ve complementado por la riqueza de matices e ideas que se van introduciendo de manera progresiva, evitando que el lector pueda verse abrumado por la avalancha de ideas y contenidos. Las preguntas de Bruno Bérard, siempre inteligentes, incisivas y pertinentes, además de ordenadas y bien estructuradas, favorecen la continuidad y el dinamismo en la exposición de los temas, ejerciendo de guía en la conversación. De ahí que el libro sea apto para diferentes niveles, tanto para aquellos que desconocen el esoterismo, como para quienes se encuentran familiarizados con el tema. Aldo La Fata, de acuerdo con su dilatada y extensa trayectoria en la materia, nos hace reflexiones teóricas de enorme valor, que entrelaza con su propia experiencia y trayectoria en el estudio del esoterismo. Sin lugar a dudas este aspecto nos permite ver una vertiente más humana e íntima, en la que se incluyen anécdotas personales y biográficas que siempre permiten una mayor conexión con el lector a través de la mezcla de hechos vitales y erudición teórica. La entrevista que nos ofrecen Bruno Bérard y Aldo La Fata nos permite explorar la relación dialéctica que se genera entre el esoterismo y otros ámbitos como la religión, la ciencia o la filosofía. Todas las cuestiones se abordan desde enfoques muy concretos, abordando problemáticas particulares, que dan lugar a reflexiones más amplias evitando las simplificaciones e invitando a reflexiones mucho más profundas. De ahí la función de introducción y guía a la que nos venimos refiriendo. Estos aspectos que acabamos de enumerar con anterioridad revelan un notable esfuerzo pedagógico por parte de los autores para acercarnos al estudio del esoterismo, nos aporta las herramientas necesarias, parafraseando el título de la obra, para discernir entre un verdadero esoterismo y sus falsificaciones. Más allá de estos aspectos formales, que consideramos que es importante destacar, porque en ellos reside el éxito de la obra, en un planteamiento que resulta original, a la par que ameno y de gran interés, debemos considerar otros aspectos que hacen más referencia al contenido. *«¿Qué es el esoterismo? Entre verdades y falsificaciones»* pretende, como decíamos, clarificar qué es el esoterismo, cuales son sus particulares, sus características y atributos, su naturaleza más íntima, como fenómeno espiritual y filosófico en sus aspectos más profundos, que podemos remontar a épocas muy remotas y lejanas en el tiempo. Pero el esoterismo aparece en ocasiones fuertemente imbricado en otras estructuras de pensamiento, de tipo tradicional, como son las grandes religiones (Cristianismo, Islam, Judaísmo etc) y otros conceptos como la mística y la metafísica, cuyas relaciones hay que desentrañar. # La importancia de René Guénon Aldo La Fata nos libera desde el principio de posibles equívocos al enfatizar que el verdadero esoterismo no es una simple acumulación de conocimientos secretos o rituales exóticos, sino una vía de trascendencia espiritual basada en el rigor y la autenticidad. A este respecto [René Guénon aparece como uno de los grandes esoteristas de nuestro tiempo](https://hiperbolajanus.com/posts/rene-guenon-y-la-civilizacion-occidental/), en la medida que fue el gran intérprete y codificador de estos conocimientos, una figura que marcó un antes y un después en la comprensión de este ámbito, especialmente por su rigor conceptual y su capacidad para distinguir entre lo auténtico y lo falso en las tradiciones espirituales. A tal respecto podemos poner como ejemplo sus contundentes análisis de las corrientes ocultistas, especialmente del espiritismo o del teosofismo, en diferentes obras. Podemos decir a este respecto que Guénon hizo una distinción entre esoterismo y ocultismo, disociando el significado del primero de prácticas superficiales y desviadas, mientras que definió el esoterismo como una vía de conocimiento sagrado y trascendente. En este sentido fue una labor fundamental para evitar confusiones con mixtificaciones modernas y pseudoesoterismos como [aquellos relacionados con el *New Age*](https://hiperbolajanus.com/posts/nom-magos-negros/). |[](https://www.hiperbolajanus.com/libros/maestro-tradicion-rene-guenon/)| |:-:| |[GUÉNON, René; _El Maestro de la Tradición Perenne: Antología de artículos guenonianos_; Hipérbola Janus, 2021](https://www.hiperbolajanus.com/libros/maestro-tradicion-rene-guenon/)| Paralelamente, y con ello queremos dignificar la figura de René Guénon, el tradicionalista francés también nos abrió las fuentes de un vasto conocimiento espiritual, expresión de una «Tradición primordial», a cuyos orígenes prístinos siempre deberíamos aspirar, y [cuya impronta impregna por completo religiones, culturas y formas de civilización no modernas](https://hiperbolajanus.com/posts/el-reino-de-la-cantidad-y-los-signos-de/), claro está. Y otro elemento fundamental, y que en la presente obra se considera de vital importancia, es que René Guénon considera el esoterismo no como una vía interna propia de la religión, sino como una vía complementaria que permite acceder a la esencia divina más allá de las formas externas. Para Aldo La Fata no se trata de una mera referencia intelectual, sino una figura que marcó su propio rumbo dentro del estudio del esoterismo. A través de obras como *Los símbolos de la ciencia sagrada*, La Fata descubrió la profundidad y la coherencia del pensamiento guenoniano, así como la idea de que el esoterismo actúa como el «pegamento» que conecta todas las tradiciones espirituales. Esta visión le permitió entender el esoterismo como algo inseparable de la religión, aunque con una profundidad y una exigencia mayores. # ¿Qué es el esoterismo? El término esoterismo tiene sus raíces etimológicas en el griego *esôterikos*, que implica un «ir hacia dentro» y que se contrapone a una variante exterior que definimos como «exoterismo», que se encuentra más vinculado al ámbito de la religión. Se trata de un conocimiento que no atiende a un principio puramente intelectual y discursivo sino que apunta a una vivencia directa y sapiencial de lo trascendente. Lejos de la acumulación de saberes ocultos y rituales, lo que prima en la experiencia de lo esotérico es la conexión directa con lo trascendente y lo divino a través de la práctica espiritual. De hecho hay tres aspectos que nuestros autores destacan a lo largo de la obra respecto al esoterismo, y que nos parecen fundamentales: - **Interioridad**: Supone un movimiento continuo hacia el interior, de exploración e introspección, en el que se tratan de derribar límites y obstáculos. Atendiendo a un dinamismo que huye de lo fijo y de lo estático. - **Profundización**: La búsqueda de significados más profundos tras la realidad cotidiana, buscando ir más allá de la pura exterioridad de las cosas - **Relación con el exoterismo**: Podemos considerarlo opuesto en sentido relativo al esoterismo, como una dimensión más externa y visible de las religiones, aunque este último (el esoterismo), no puede sobrevivir sin el apoyo de una tradición religiosa. En relación al último punto debemos destacar, como advierten Bérard y La Fata, que pese a todo no podemos entender el esoterismo como una parte de las religiones, sino que tiene su propia función y objetivos, que no es otro que el que ya hemos mencionado con anterioridad: establecer una conexión directa con la verdad que irradia del principio universal y divino. |[](https://www.hiperbolajanus.com/libros/pensamiento_esoterico_leonardo_vinci_paul_vulliaud/)| |:-:| |[VULLIAUD, Paul; _El pensamiento esotérico de Leonardo da Vinci_; Hipérbola Janus, 2024](https://www.hiperbolajanus.com/libros/pensamiento_esoterico_leonardo_vinci_paul_vulliaud/)| Otro aspecto interesante de la obra es el que nos habla de [las relaciones entre esoterismo y metafísica](https://hiperbolajanus.com/libros/metapolitica-tradicion-modernidad-julius-evola/), en el que el primero pretende ser también una vía de acceso al dominio del segundo. El esoterismo, como ya hemos visto, tiene como principal propósito trascender las categorías del mundo material para proyectarse en lo universal, y en este sentido comparte también objetivos con la metafísica, que pretende superar las limitaciones de la experiencia humana ordinaria y de acceder a las verdades primordiales que estructuran la realidad. Ambos apuntan a la raíz de todo lo existente, al absoluto. Las divergencias las hallamos en la forma o en el método para alcanzar estas verdades trascendentes, que en el caso del esoterismo nos remiten a símbolos, rituales y experiencias vivenciales que permiten al practicante interiorizar verdades universales. De este modo, esoterismo y metafísica se nos presentan como realidades no opuestas, sino complementarias. La metafísica nos ofrece un marco conceptual y doctrinal para entender lo absoluto, mientras que el esoterismo se centra en su realización interna. En términos guenonianos, el esoterismo representa los aspectos operativos de la metafísica. De modo que podemos decir que la metafísica aborda el tema trascendente desde una perspectiva conceptual, sin esa parte vivida de la experiencia en el conocimiento de lo universal. El esoterismo, por su parte, aporta esa contraparte que nos remite a la experiencia humana que permite al individuo acceder o ponerse en conexión con lo divino a través de su propio ser, de manera directa y vívida. Es un camino que el sujeto individual emprende para lograr una transformación interior. Paralelamente, no podemos obviar dentro de todos estos procesos la participación de un elemento fundamental, como es la intuición suprarracional, que podríamos considerar como la herramienta que conecta al esoterista directamente con la fuente del conocimiento trascendente y universal, en lugar de hacerlo directamente a través de teorías o conceptos que siempre resultan más abstractos y difíciles de comprender en su vertiente más «discursiva». Al mismo tiempo, las relaciones que se establecen entre esoterismo y metafísica nos permiten poner en contacto las tradiciones religiosas con el conocimiento universal. Según La Fata, inspirándose en el legado de la obra de Frithjoff Schuon, cada tradición espiritual tiene una dimensión metafísica que puede ser comprendida y realizada a través del esoterismo, como un medio para acceder a la esencia inmutable de todas las formas religiosas. Otro aspecto que esoterismo y metafísica comparten es la meta de superar la dualidad entre sujeto y objeto: Mientras que la metafísica conceptualiza esta unión como una verdad última, el esoterismo busca experimentarla directamente a través de la contemplación, el símbolo y la práctica espiritual. # Los autores || |:-:| |Aldo La Fata| Aldo La Fata (1964) es un estudioso del esoterismo, el simbolismo y la mística religiosa, con una trayectoria de varias décadas dedicada al análisis y divulgación de estas disciplinas. Ha sido jefe de redacción de la revista *Metapolitica*, fundada por **Silvano Panunzio**, y actualmente dirige *Il Corriere Metapolitico*. Su trabajo destaca por una aproximación rigurosa y una mirada crítica a las corrientes contemporáneas del esoterismo, rescatando su sentido más profundo y tradicional. Entre sus obras más relevantes se encuentran *Silvano Panunzio: vita e pensiero* (2021) y *Nella luce dei libri* (2022), donde explora la intersección entre espiritualidad, simbolismo y pensamiento tradicional. || |:-:| |Bruno Bérard| Bruno Bérard (1958), es doctor en Religiones y Sistemas de Pensamiento por la École Pratique des Hautes Études (EPHE), es un destacado especialista en metafísica. Autor de múltiples ensayos, ha desarrollado una profunda reflexión sobre la naturaleza del conocimiento espiritual y su relación con las tradiciones religiosas. Algunas de sus obras más importantes, traducidas a diversas lenguas, incluyen A *Metaphysics of the Christian Mystery* (2018) y *Métaphysique du paradoxe* (2019). Actualmente, dirige la colección *Métaphysique au quotidien* en la editorial L’Harmattan de París, consolidándose como una referencia en el estudio de la metafísica contemporánea. En *¿Qué es el esoterismo?: Entre verdades y falsificaciones*, asistimos a una presentación del tema tratado desde un conocimiento profundo y dilatado del tema, en la que ambos autores combinan la experiencia y el conocimiento que atesoran sobre el esoterismo y otros temas anejos, ofreciéndonos sus interpretaciones y enfoques particulares, y al mismo tiempo mostrando una gran capacidad de síntesis en la exposición de los temas tratados, que se inscriben en una multitud de tradiciones religiosas y espirituales de enorme complejidad. En este último punto reside también gran parte del valor de la obra, que constituye una novedad editorial especialmente relevante en su ámbito en lengua hispana. --- **Artículo original**: Hipérbola Janus, [_Presentación de «¿Qué es el esoterismo?: Entre verdades y falsificaciones»_](https://www.hiperbolajanus.com/posts/presentacion-esoterismo-berard-lafata/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/presentacion-esoterismo-berard-lafata/), 6/Feb/2025
@ bcbb3e40:a494e501
2025-03-31 15:23:12|[](https://www.hiperbolajanus.com/libros/esoterismo-berard-fata/)| |:-:| |[BÉRARD, Bruno y LA FATA, Aldo; _¿Qué es el esoterismo?: Entre verdades y falsificacioines_; Hipérbola Janus, 2025](https://hiperbolajanus.com/libros/esoterismo-berard-fata/)| Nos complace presentar al lector en lengua española una novedad de primer orden, y sobre un tema que viene siendo objeto de interés por parte de nuestra línea editorial, como es el esoterismo, que hemos abordado recientemente a través de un nuevo recopilatorio de la obra evoliana en [*Ensayos filosóficos, esotéricos y religiosos 1925-1931*](https://hiperbolajanus.com/posts/presentacion-ensayos-filosoficos-evola/), donde hemos tratado de rescatar los textos de las primeras etapas en la formulación del pensamiento del Maestro Romano. No obstante, no es la primera aventura que hemos emprendido en este terreno, siempre complejo y acompañado de la etiqueta, popular y quizás vulgarizada, de lo «misterioso» y lo «oculto», aunque no somos nada sospechosos en ese sentido por banalizar o tratar de ofrecer un enfoque puramente literario del asunto, y ni mucho menos de simpatizar con aquellas vías que entroncan con el *New age*, donde las mixtificaciones y la voluntad de convertir el fenómeno esotérico en un producto de consumo más, como demanda el mercado, para satisfacer demandas materiales o simples modas de una masa sobresocializada son norma habitual. Podríamos citar multitud de obras que están presentes en nuestro catálogo, como son [*El pensamiento esotérico de Leonardo*](https://hiperbolajanus.com/posts/presentacion-pensamiento-esoterico-leonardo-paul-vulliaud/), de **Paul Vulliaud**, [*El mundo mágico de los héroes*](https://hiperbolajanus.com/posts/mundo-magico-heroes-cesare-riviera/), de **Cesare della Riviera**, una joya del esoterismo italiano del siglo XVII, en [*El maestro de la tradición perenne*](https://hiperbolajanus.com/posts/rene-guenon-maestro-tradicion-perenne/), de **René Guénon**, o en el ensayo de **Gianluca Marletta** [*OVNIS y alienígenas. Origen, historia y prodigio de una pseudorreligión*](https://hiperbolajanus.com/posts/ovnis-alienigenas-gianluca-marletta/), un ensayo de notable originalidad donde se abordan aspectos esotéricos, aunque sea de un modo más tangencial. También en la literatura, con la obra del gran mitólogo y literato **Boris Nad**, [*Una historia de Agartha*](https://hiperbolajanus.com/posts/historia-agartha-boris-nad/) y [*La muerte púrpura*](https://hiperbolajanus.com/posts/gustav-meyrink/) de **Gustav Meyrink** encontramos nuevas referencias al ámbito esotérico. De modo que podemos concluir en que el esoterismo forma parte esencial de nuestras publicaciones e intereses como editores, y contribuimos activamente a su difusión. |[](https://www.hiperbolajanus.com/libros/ensayos-filosoficos-esotericos-religiosos-evola/)| |:-:| |[EVOLA, Julius; _Ensayos filosóficos, esotéricos y religiosos: 1925-1931_, Hiperbola Janus, 2024](https://www.hiperbolajanus.com/libros/ensayos-filosoficos-esotericos-religiosos-evola/)| # Una obra original Por eso la presente obra, la que nos disponemos a presentar, cuyo título es *¿Qué es el esoterismo?: Entre verdades y falsificaciones*, de **Bruno Bérard** y **Aldo La Fata**, viene a ser una obra muy necesaria y clarificadora en la comprensión del esoterismo en todas sus dimensiones, en la complejidad de sus particulares, y en sus múltiples manifestaciones. Quizás en el mundo de habla hispana el esoterismo es un fenómeno que no ha obtenido su merecida atención, y nuestros autores en este ámbito, como es el caso de un **Ramón Llull** entre otros, no sean objeto de la atención que merece, y las actividades esotéricas, a nivel de asociaciones, comunidades u otras formas de organización, tampoco sean especialmente conocidas, ni cuenten con una actividad reconocida. Es posible, como señala La Fata, que haya ciertas reticencias dentro del mundo católico, acostumbrado a la ortodoxia y la guía espiritual de la Iglesia, y que cualquier tipo de «desviación» hacia formas más individuales y «libres» de vivir ciertas formas iniciáticas, mucho más sutiles, provoquen el rechazo y la incomprensión general. No obstante, como también se encargan de aclarar nuestros autores, el esoterismo comprende una dimensión diferenciada, implica un esfuerzo que no todos están dispuestos a acometer, y finalmente, no es tampoco un camino de felicidad y de frutos seguros, implica una transformación interior y la asunción de unas prácticas y procedimientos que no son aptos para cualquiera. Digamos que el esoterismo es un camino, una vía, que a diferencia de las «religiones populares», exotéricas, supone un arduo camino que viene marcado por un principio vertical y aristocrático de la existencia, o al menos así queremos verlo nosotros. El incremento de la capacidad de discernimiento, aunar lo visible con lo invisible, y ser capaz de superar límites vedados al común, no por simple vanidad ni por «crecimiento personal», tal y como se concibe en las aburguesadas y decadentes sociedades actuales, sino como parte de un proceso de aprendizaje, de autoconocimiento y de liberación. No nos cabe duda alguna de la necesidad de restaurar los antiguos vínculos con lo Alto, las vías que quedaron cerradas y que nos han limitado progresivamente al exclusivo y estrecho ámbito de la materialidad. |[](https://www.hiperbolajanus.com/libros/mundo-magico-heroes-cesare-riviera/)| |:-:| |[RIVIERA, Cesare della; _El mundo mágico de los héroes_; Hipérbola Janus, 2022](https://www.hiperbolajanus.com/libros/mundo-magico-heroes-cesare-riviera/)| La obra emplea el recurso de la entrevista/diálogo, que aporta frescura y fluidez al texto «simplificando», o más bien haciendo más accesibles y comprensibles elementos relacionados con el esoterismo, que de otro modo resultarían excesivamente complejos para una parte del público lector poco familiarizado con la materia. Este dinamismo se ve complementado por la riqueza de matices e ideas que se van introduciendo de manera progresiva, evitando que el lector pueda verse abrumado por la avalancha de ideas y contenidos. Las preguntas de Bruno Bérard, siempre inteligentes, incisivas y pertinentes, además de ordenadas y bien estructuradas, favorecen la continuidad y el dinamismo en la exposición de los temas, ejerciendo de guía en la conversación. De ahí que el libro sea apto para diferentes niveles, tanto para aquellos que desconocen el esoterismo, como para quienes se encuentran familiarizados con el tema. Aldo La Fata, de acuerdo con su dilatada y extensa trayectoria en la materia, nos hace reflexiones teóricas de enorme valor, que entrelaza con su propia experiencia y trayectoria en el estudio del esoterismo. Sin lugar a dudas este aspecto nos permite ver una vertiente más humana e íntima, en la que se incluyen anécdotas personales y biográficas que siempre permiten una mayor conexión con el lector a través de la mezcla de hechos vitales y erudición teórica. La entrevista que nos ofrecen Bruno Bérard y Aldo La Fata nos permite explorar la relación dialéctica que se genera entre el esoterismo y otros ámbitos como la religión, la ciencia o la filosofía. Todas las cuestiones se abordan desde enfoques muy concretos, abordando problemáticas particulares, que dan lugar a reflexiones más amplias evitando las simplificaciones e invitando a reflexiones mucho más profundas. De ahí la función de introducción y guía a la que nos venimos refiriendo. Estos aspectos que acabamos de enumerar con anterioridad revelan un notable esfuerzo pedagógico por parte de los autores para acercarnos al estudio del esoterismo, nos aporta las herramientas necesarias, parafraseando el título de la obra, para discernir entre un verdadero esoterismo y sus falsificaciones. Más allá de estos aspectos formales, que consideramos que es importante destacar, porque en ellos reside el éxito de la obra, en un planteamiento que resulta original, a la par que ameno y de gran interés, debemos considerar otros aspectos que hacen más referencia al contenido. *«¿Qué es el esoterismo? Entre verdades y falsificaciones»* pretende, como decíamos, clarificar qué es el esoterismo, cuales son sus particulares, sus características y atributos, su naturaleza más íntima, como fenómeno espiritual y filosófico en sus aspectos más profundos, que podemos remontar a épocas muy remotas y lejanas en el tiempo. Pero el esoterismo aparece en ocasiones fuertemente imbricado en otras estructuras de pensamiento, de tipo tradicional, como son las grandes religiones (Cristianismo, Islam, Judaísmo etc) y otros conceptos como la mística y la metafísica, cuyas relaciones hay que desentrañar. # La importancia de René Guénon Aldo La Fata nos libera desde el principio de posibles equívocos al enfatizar que el verdadero esoterismo no es una simple acumulación de conocimientos secretos o rituales exóticos, sino una vía de trascendencia espiritual basada en el rigor y la autenticidad. A este respecto [René Guénon aparece como uno de los grandes esoteristas de nuestro tiempo](https://hiperbolajanus.com/posts/rene-guenon-y-la-civilizacion-occidental/), en la medida que fue el gran intérprete y codificador de estos conocimientos, una figura que marcó un antes y un después en la comprensión de este ámbito, especialmente por su rigor conceptual y su capacidad para distinguir entre lo auténtico y lo falso en las tradiciones espirituales. A tal respecto podemos poner como ejemplo sus contundentes análisis de las corrientes ocultistas, especialmente del espiritismo o del teosofismo, en diferentes obras. Podemos decir a este respecto que Guénon hizo una distinción entre esoterismo y ocultismo, disociando el significado del primero de prácticas superficiales y desviadas, mientras que definió el esoterismo como una vía de conocimiento sagrado y trascendente. En este sentido fue una labor fundamental para evitar confusiones con mixtificaciones modernas y pseudoesoterismos como [aquellos relacionados con el *New Age*](https://hiperbolajanus.com/posts/nom-magos-negros/). |[](https://www.hiperbolajanus.com/libros/maestro-tradicion-rene-guenon/)| |:-:| |[GUÉNON, René; _El Maestro de la Tradición Perenne: Antología de artículos guenonianos_; Hipérbola Janus, 2021](https://www.hiperbolajanus.com/libros/maestro-tradicion-rene-guenon/)| Paralelamente, y con ello queremos dignificar la figura de René Guénon, el tradicionalista francés también nos abrió las fuentes de un vasto conocimiento espiritual, expresión de una «Tradición primordial», a cuyos orígenes prístinos siempre deberíamos aspirar, y [cuya impronta impregna por completo religiones, culturas y formas de civilización no modernas](https://hiperbolajanus.com/posts/el-reino-de-la-cantidad-y-los-signos-de/), claro está. Y otro elemento fundamental, y que en la presente obra se considera de vital importancia, es que René Guénon considera el esoterismo no como una vía interna propia de la religión, sino como una vía complementaria que permite acceder a la esencia divina más allá de las formas externas. Para Aldo La Fata no se trata de una mera referencia intelectual, sino una figura que marcó su propio rumbo dentro del estudio del esoterismo. A través de obras como *Los símbolos de la ciencia sagrada*, La Fata descubrió la profundidad y la coherencia del pensamiento guenoniano, así como la idea de que el esoterismo actúa como el «pegamento» que conecta todas las tradiciones espirituales. Esta visión le permitió entender el esoterismo como algo inseparable de la religión, aunque con una profundidad y una exigencia mayores. # ¿Qué es el esoterismo? El término esoterismo tiene sus raíces etimológicas en el griego *esôterikos*, que implica un «ir hacia dentro» y que se contrapone a una variante exterior que definimos como «exoterismo», que se encuentra más vinculado al ámbito de la religión. Se trata de un conocimiento que no atiende a un principio puramente intelectual y discursivo sino que apunta a una vivencia directa y sapiencial de lo trascendente. Lejos de la acumulación de saberes ocultos y rituales, lo que prima en la experiencia de lo esotérico es la conexión directa con lo trascendente y lo divino a través de la práctica espiritual. De hecho hay tres aspectos que nuestros autores destacan a lo largo de la obra respecto al esoterismo, y que nos parecen fundamentales: - **Interioridad**: Supone un movimiento continuo hacia el interior, de exploración e introspección, en el que se tratan de derribar límites y obstáculos. Atendiendo a un dinamismo que huye de lo fijo y de lo estático. - **Profundización**: La búsqueda de significados más profundos tras la realidad cotidiana, buscando ir más allá de la pura exterioridad de las cosas - **Relación con el exoterismo**: Podemos considerarlo opuesto en sentido relativo al esoterismo, como una dimensión más externa y visible de las religiones, aunque este último (el esoterismo), no puede sobrevivir sin el apoyo de una tradición religiosa. En relación al último punto debemos destacar, como advierten Bérard y La Fata, que pese a todo no podemos entender el esoterismo como una parte de las religiones, sino que tiene su propia función y objetivos, que no es otro que el que ya hemos mencionado con anterioridad: establecer una conexión directa con la verdad que irradia del principio universal y divino. |[](https://www.hiperbolajanus.com/libros/pensamiento_esoterico_leonardo_vinci_paul_vulliaud/)| |:-:| |[VULLIAUD, Paul; _El pensamiento esotérico de Leonardo da Vinci_; Hipérbola Janus, 2024](https://www.hiperbolajanus.com/libros/pensamiento_esoterico_leonardo_vinci_paul_vulliaud/)| Otro aspecto interesante de la obra es el que nos habla de [las relaciones entre esoterismo y metafísica](https://hiperbolajanus.com/libros/metapolitica-tradicion-modernidad-julius-evola/), en el que el primero pretende ser también una vía de acceso al dominio del segundo. El esoterismo, como ya hemos visto, tiene como principal propósito trascender las categorías del mundo material para proyectarse en lo universal, y en este sentido comparte también objetivos con la metafísica, que pretende superar las limitaciones de la experiencia humana ordinaria y de acceder a las verdades primordiales que estructuran la realidad. Ambos apuntan a la raíz de todo lo existente, al absoluto. Las divergencias las hallamos en la forma o en el método para alcanzar estas verdades trascendentes, que en el caso del esoterismo nos remiten a símbolos, rituales y experiencias vivenciales que permiten al practicante interiorizar verdades universales. De este modo, esoterismo y metafísica se nos presentan como realidades no opuestas, sino complementarias. La metafísica nos ofrece un marco conceptual y doctrinal para entender lo absoluto, mientras que el esoterismo se centra en su realización interna. En términos guenonianos, el esoterismo representa los aspectos operativos de la metafísica. De modo que podemos decir que la metafísica aborda el tema trascendente desde una perspectiva conceptual, sin esa parte vivida de la experiencia en el conocimiento de lo universal. El esoterismo, por su parte, aporta esa contraparte que nos remite a la experiencia humana que permite al individuo acceder o ponerse en conexión con lo divino a través de su propio ser, de manera directa y vívida. Es un camino que el sujeto individual emprende para lograr una transformación interior. Paralelamente, no podemos obviar dentro de todos estos procesos la participación de un elemento fundamental, como es la intuición suprarracional, que podríamos considerar como la herramienta que conecta al esoterista directamente con la fuente del conocimiento trascendente y universal, en lugar de hacerlo directamente a través de teorías o conceptos que siempre resultan más abstractos y difíciles de comprender en su vertiente más «discursiva». Al mismo tiempo, las relaciones que se establecen entre esoterismo y metafísica nos permiten poner en contacto las tradiciones religiosas con el conocimiento universal. Según La Fata, inspirándose en el legado de la obra de Frithjoff Schuon, cada tradición espiritual tiene una dimensión metafísica que puede ser comprendida y realizada a través del esoterismo, como un medio para acceder a la esencia inmutable de todas las formas religiosas. Otro aspecto que esoterismo y metafísica comparten es la meta de superar la dualidad entre sujeto y objeto: Mientras que la metafísica conceptualiza esta unión como una verdad última, el esoterismo busca experimentarla directamente a través de la contemplación, el símbolo y la práctica espiritual. # Los autores || |:-:| |Aldo La Fata| Aldo La Fata (1964) es un estudioso del esoterismo, el simbolismo y la mística religiosa, con una trayectoria de varias décadas dedicada al análisis y divulgación de estas disciplinas. Ha sido jefe de redacción de la revista *Metapolitica*, fundada por **Silvano Panunzio**, y actualmente dirige *Il Corriere Metapolitico*. Su trabajo destaca por una aproximación rigurosa y una mirada crítica a las corrientes contemporáneas del esoterismo, rescatando su sentido más profundo y tradicional. Entre sus obras más relevantes se encuentran *Silvano Panunzio: vita e pensiero* (2021) y *Nella luce dei libri* (2022), donde explora la intersección entre espiritualidad, simbolismo y pensamiento tradicional. || |:-:| |Bruno Bérard| Bruno Bérard (1958), es doctor en Religiones y Sistemas de Pensamiento por la École Pratique des Hautes Études (EPHE), es un destacado especialista en metafísica. Autor de múltiples ensayos, ha desarrollado una profunda reflexión sobre la naturaleza del conocimiento espiritual y su relación con las tradiciones religiosas. Algunas de sus obras más importantes, traducidas a diversas lenguas, incluyen A *Metaphysics of the Christian Mystery* (2018) y *Métaphysique du paradoxe* (2019). Actualmente, dirige la colección *Métaphysique au quotidien* en la editorial L’Harmattan de París, consolidándose como una referencia en el estudio de la metafísica contemporánea. En *¿Qué es el esoterismo?: Entre verdades y falsificaciones*, asistimos a una presentación del tema tratado desde un conocimiento profundo y dilatado del tema, en la que ambos autores combinan la experiencia y el conocimiento que atesoran sobre el esoterismo y otros temas anejos, ofreciéndonos sus interpretaciones y enfoques particulares, y al mismo tiempo mostrando una gran capacidad de síntesis en la exposición de los temas tratados, que se inscriben en una multitud de tradiciones religiosas y espirituales de enorme complejidad. En este último punto reside también gran parte del valor de la obra, que constituye una novedad editorial especialmente relevante en su ámbito en lengua hispana. --- **Artículo original**: Hipérbola Janus, [_Presentación de «¿Qué es el esoterismo?: Entre verdades y falsificaciones»_](https://www.hiperbolajanus.com/posts/presentacion-esoterismo-berard-lafata/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/presentacion-esoterismo-berard-lafata/), 6/Feb/2025 @ 9e69e420:d12360c2
2025-01-30 12:13:39Salwan Momika, a Christian Iraqi known for burning the Koran in Sweden, was shot dead during a TikTok livestream in an apartment in Sodertalje. The 38-year-old sparked outrage in the Muslim community for his demonstrations, leading to global condemnation. After being rushed to the hospital, he was pronounced dead. Authorities arrested five individuals in connection with the incident. Momika's death comes days before a court ruling on his possible incitement of ethnic hatred. The incident highlights the tensions surrounding free speech and religious sentiments, intensifying after his controversial protests in 2023. [Sauce](https://www.dailymail.co.uk/news/article-14341423/Christian-Iraqi-burnt-Koran-Sweden-shot-dead.html)
@ 9e69e420:d12360c2
2025-01-30 12:13:39Salwan Momika, a Christian Iraqi known for burning the Koran in Sweden, was shot dead during a TikTok livestream in an apartment in Sodertalje. The 38-year-old sparked outrage in the Muslim community for his demonstrations, leading to global condemnation. After being rushed to the hospital, he was pronounced dead. Authorities arrested five individuals in connection with the incident. Momika's death comes days before a court ruling on his possible incitement of ethnic hatred. The incident highlights the tensions surrounding free speech and religious sentiments, intensifying after his controversial protests in 2023. [Sauce](https://www.dailymail.co.uk/news/article-14341423/Christian-Iraqi-burnt-Koran-Sweden-shot-dead.html) @ 0fa80bd3:ea7325de
2025-01-30 04:28:30**"Degeneration"** or **"Вырождение"** ![[photo_2025-01-29 23.23.15.jpeg]] A once-functional object, now eroded by time and human intervention, stripped of its original purpose. Layers of presence accumulate—marks, alterations, traces of intent—until the very essence is obscured. Restoration is paradoxical: to reclaim, one must erase. Yet erasure is an impossibility, for to remove these imprints is to deny the existence of those who shaped them. The work stands as a meditation on entropy, memory, and the irreversible dialogue between creation and decay.
@ 0fa80bd3:ea7325de
2025-01-30 04:28:30**"Degeneration"** or **"Вырождение"** ![[photo_2025-01-29 23.23.15.jpeg]] A once-functional object, now eroded by time and human intervention, stripped of its original purpose. Layers of presence accumulate—marks, alterations, traces of intent—until the very essence is obscured. Restoration is paradoxical: to reclaim, one must erase. Yet erasure is an impossibility, for to remove these imprints is to deny the existence of those who shaped them. The work stands as a meditation on entropy, memory, and the irreversible dialogue between creation and decay. @ 0fa80bd3:ea7325de
2025-01-29 15:43:42Lyn Alden - биткойн евангелист или евангелистка, я пока не понял ``` npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83a ``` Thomas Pacchia - PubKey owner - X - @tpacchia ``` npub1xy6exlg37pw84cpyj05c2pdgv86hr25cxn0g7aa8g8a6v97mhduqeuhgpl ``` calvadev - Shopstr ``` npub16dhgpql60vmd4mnydjut87vla23a38j689jssaqlqqlzrtqtd0kqex0nkq ``` Calle - Cashu founder ``` npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vg ``` Джек Дорси ``` npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m ``` 21 ideas ``` npub1lm3f47nzyf0rjp6fsl4qlnkmzed4uj4h2gnf2vhe3l3mrj85vqks6z3c7l ``` Много адресов. Хз кто надо сортировать ``` https://github.com/aitechguy/nostr-address-book ``` ФиатДжеф - создатель Ностр - https://github.com/fiatjaf ``` npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 ``` EVAN KALOUDIS Zues wallet ``` npub19kv88vjm7tw6v9qksn2y6h4hdt6e79nh3zjcud36k9n3lmlwsleqwte2qd ``` Программер Коди https://github.com/CodyTseng/nostr-relay ``` npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl ``` Anna Chekhovich - Managing Bitcoin at The Anti-Corruption Foundation https://x.com/AnyaChekhovich ``` npub1y2st7rp54277hyd2usw6shy3kxprnmpvhkezmldp7vhl7hp920aq9cfyr7 ```
@ 0fa80bd3:ea7325de
2025-01-29 15:43:42Lyn Alden - биткойн евангелист или евангелистка, я пока не понял ``` npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83a ``` Thomas Pacchia - PubKey owner - X - @tpacchia ``` npub1xy6exlg37pw84cpyj05c2pdgv86hr25cxn0g7aa8g8a6v97mhduqeuhgpl ``` calvadev - Shopstr ``` npub16dhgpql60vmd4mnydjut87vla23a38j689jssaqlqqlzrtqtd0kqex0nkq ``` Calle - Cashu founder ``` npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vg ``` Джек Дорси ``` npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m ``` 21 ideas ``` npub1lm3f47nzyf0rjp6fsl4qlnkmzed4uj4h2gnf2vhe3l3mrj85vqks6z3c7l ``` Много адресов. Хз кто надо сортировать ``` https://github.com/aitechguy/nostr-address-book ``` ФиатДжеф - создатель Ностр - https://github.com/fiatjaf ``` npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 ``` EVAN KALOUDIS Zues wallet ``` npub19kv88vjm7tw6v9qksn2y6h4hdt6e79nh3zjcud36k9n3lmlwsleqwte2qd ``` Программер Коди https://github.com/CodyTseng/nostr-relay ``` npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl ``` Anna Chekhovich - Managing Bitcoin at The Anti-Corruption Foundation https://x.com/AnyaChekhovich ``` npub1y2st7rp54277hyd2usw6shy3kxprnmpvhkezmldp7vhl7hp920aq9cfyr7 ``` @ bcbb3e40:a494e501
2025-03-31 15:02:58Traducción por Francisco de la Torre. || |:-:| |Los representantes de la derecha sionista europea que forman parte de «Patriots» reunidos en Bruselas el pasado mes de diciembre de 2024.| Entre los efectos que probablemente producirá en Europa la nueva administración estadounidense, es previsible [el fortalecimiento del ala derecha del colaboracionismo atlantista](https://hiperbolajanus.com/posts/mos-maiorum-8/) que, después de haberse posicionado decididamente a favor de Donald Trump durante su presidencia 2017-2021, en el transcurso de la administración Biden abogó fervientemente por su regreso a la Casa Blanca y acogió su victoria electoral con gran júbilo. A finales de octubre de 2024, en el grandioso [mitin preelectoral a favor de Trump](https://hiperbolajanus.com/posts/adios-woke-que-viene-ahora/) celebrado en el Madison Square Garden de Nueva York, asistió una representante del grupo parlamentario europeo *Patriots for Europe*, que viajó a Estados Unidos para esa ocasión especial. En un vídeo publicado en la página X (antes twitter) de los *Patriots*, varios eurodiputados del mencionado grupo expresaron su identidad con los puntos de vista de Trump y auspiciando su reelección: el austriaco Harald Vilimsky (*Freiheitliche Partei Österreichs*), el checo Ondrej Knotek (*Año 2011*) el español Jorge Buxade (*Vox*), el holandés Tom Vandendriesche (*Vlaams Belang*), la polaca Anna Bryłka (*Ruch Narodowy*) y, por Hungría, Tamás Deutsch (*Fidesz*). Este último es, sin duda, la personalidad más eminente del grupo de los *Patriots* que viajaron a Nueva York: originario de una familia judía de Budapest, en 1988 Tamás Deutsch junto con Viktor Orbán están entre los fundadores de *Fidesz* —*Fiatal Demokraták Szövetsége* (Alianza de los jóvenes demócratas), en la que ocupó el cargo de vicepresidente. El *Fidesz* ha tejido durante mucho tiempo una red de lazos con el Partido Republicano de los Estados Unidos y con el think tank conservador *Heritage Foundation*, mientras que el gobierno de Viktor Orbán organizó las tres últimas ediciones anuales de la CPAC en Hungría (*Conservative Political Action Conference*), un encuentro de políticos de derechas de varios países[^1]. *Patriots for Europe* o *Patriots.eu*, denominación que recuerda al de los misiles aire-tierra estadounidenses (el *MIM-104 Patriots*), es, por tanto, el nombre oficial del grupo político de la derecha liberal-conservadora, populista y euroescéptica, nacido en julio de 2024 (primero como alianza y luego como grupo parlamentario europeo) por iniciativa del primer ministro húngaro Viktor Orbán, el exprimer ministro checo Andrej Babiŝ y del exministro del interior austriaco Herbert Kickl. Como representantes de sus respectivos partidos (*Fidesz*, *Año 2011*, *Freiheitliche Partei Österreichs*), Orbán, Babiŝ y Kickl firmaron un texto ideológico titulado: *A Patriotic Manifesto for a European Future*[^2], según la cual la única política europea legítima es aquella que, enraizada en la pluralidad de las diferentes naciones, proteja su herencia grecorromana-judeocristiana preservando su identidad, tradiciones y costumbres. Al núcleo inicial de los *Patriots* se unió el partido portugués *¡Arriva!* (*¡Chega!*), el Partido húngaro Popular Demócrata Cristiano (*Kereszténydemokrata Néppárt*), el partido español *Vox*, el Partido por la Libertad (*Partij voor de Vrijheid*) holandés, el Partido Popular Danés (*Dansk Folkeparti*), el interés Flamenco (*Vlaams Belang*), la Reunión Nacional (*Rassemblement National*) francés y, por Italia, la Liga para Primer Ministro Salvini. Constituido formalmente, el grupo parlamentario recibió una posterior adhesión del diputado griego de *Voz de la Razón* (*Foní Logikis*), del diputado de *Primero Letonia* (*Letvija pirmajâ prohibir*), de los dos diputados del Movimiento Nacional polaco (*Ruch Narodowy*) y de los dos diputados checos del Juramento (*Přísaha*) y de los Automovilistas por sí mismos (*Motoristé sollozoê*). Presidente del grupo parlamentario *Patriots.eu*, que cuenta con un total de ochenta y seis diputados[^3], es Jordan Bardella, presidente de la *Rassemblement National*; pero la personalidad más notable y prestigiosa de los *Patriots* es, sin duda, el primer ministro húngaro Viktor Orbán. En cuanto a la línea de política exterior seguida por Viktor Orbán, cabe recordar que fue durante su primer mandato, en 1989, cuando Hungría se unió a la OTAN junto con la República Checa y Polonia. La pertenencia a la organización militar de la Alianza Atlántica implicó la participación húngara en la guerra de Kosovo en Yugoslavia, así como la contribución de Hungría en las misiones de la ISAF y en la guerra en Irak en apoyo de la intervención estadounidense. Por otro lado, no deja de ser significativo que en junio de 2011, durante la visita de Condoleezza Rice a Budapest, se inaugurara una estatua del presidente estadounidense Ronald Reagan en la céntrica Plaza de la Libertad (*Szabadság tér*). «Hoy —dijo Orbán en esa ocasión— erigimos aquí una estatua al hombre, al líder, que cambió y renovó este mundo [creando un nuevo mundo para nosotros en Europa Central](https://hiperbolajanus.com/posts/presentacion-despues-virus-boris-nad/), un hombre que creía en la libertad, en la fuerza moral de los hombres libres, y creía que los muros que obstruyen el camino a la libertad pueden ser derribados». En los años de la primera administración Trump, Orbán estableció una relación privilegiada con la Casa Blanca: en 2019 fue recibido calurosamente por el presidente estadounidense, quien [declaró su apoyo al «soberanismo» europeo,](https://hiperbolajanus.com/libros/mos-maiorum-7/) del que Orbán era ya el exponente más puntero. El primer ministro húngaro, que más tarde expresó varias veces la esperanza de volver a ver a Trump como líder de los Estados Unidos, se reunió con él de nuevo en Mar-a-Lago de Palm Beach en marzo de 2024 y al final de la visita escribió en una publicación: «¡Hacer que América vuelva a ser grande, señor presidente!»[^4]. El entendimiento entre Trump y Orbán fue favorecido por Benjamin Netanyahu, quien ha tenido una estrecha relación con el actual primer ministro húngaro desde 2005, cuando Orbán estaba en la oposición y Netanyahu era ministro de Finanzas. Esta relación, que Orbán ha utilizado para neutralizar las iniciativas hostiles de las ONG’s de Soros (quien financió a *Fidesz* desde 1992 a 1999), ha acentuado progresivamente la posición proisraelí de Budapest, hasta el punto que Hungría junto a Austria, Croacia y República Checa, se han alineado con Estados Unidos e Israel votando en contra de la resolución propuesta por la ONU para el alto el fuego en la Franja de Gaza. Cuando László Toroczkai, jefe del partido *Mi Hazánk* (Nuestra Patria), preguntó a Orbán en el Parlamento por qué Hungría había votado en contra, el primer ministro le respondió: «La política exterior es complicada, enfréntate solo si entiendes de lo que estamos hablando»[^5]. El presidente de *Patriots*, Jordan Bardella, no es menos pro-sionista. «Reconocer un Estado palestino significaría reconocer el terrorismo», dijo Bardella, quien antes de las elecciones francesas había asegurado que, si llegaba a ser primer ministro, sería «un escudo para los compatriotas judíos contra un islamismo que no solo quiere separar la República, sino conquistarla»[^6]. Por su parte, Marine Le Pen, madrina política de Bardella, declaró: «Es absolutamente legítimo que Israel quiera erradicar al grupo terrorista armado Hamas y que se dote de medios para hacerlo»[^7]. En cuanto a la Liga de Salvini como primer ministro, sus posiciones pro-trumpistas y pro-sionistas siempre se han caracterizado por un extremismo descarado. «Nunca he ocultado —dijo Salvini antes de las elecciones estadounidenses— mi esperanza en una victoria republicana, por mil razones (...) hablamos [con Trump] a más tardar hace unas semanas. Nunca he ocultado mi simpatía humana y mi sintonía cultural»[^8]. Y sobre el genocidio en curso en Palestina, Salvini dijo: «Nuestros pensamientos están con el pueblo israelí (...) Recordar siempre el derecho de Israel a existir, a defenderse y a convivir finalmente en paz con sus pueblos vecinos, contra el horror del terrorismo islámico»[^9]. El 6 de octubre de 2024, al final de su discurso desde el escenario de Pontida, Salvini posó para una foto con los *Patriots* presentes en la manifestación de la Liga Norte: además de Viktor Orbán, estuvieron el holandés Geert Wilders, el portugués André Ventura, la austriaca Marlene Svazek, el español Antonio Fúster y el general Roberto Vannacci. Enviaron mensajes en vídeo de apoyo y solidaridad tanto Jordán Bardella en nombre de *Rassemblement national* como el ex-presidente brasileño Jair Bolsonaro. También Geert Wilders (*Partij voor de Vrijheid*), que en 2009 recibió el Premio Oriana Fallaci por producir un cortometraje de propaganda antiislámica, es conocido también por su extremismo prosionista. «Jerusalén, Judea y Samaria —en su opinión— son todas de Israel (...) La patria de los palestinos es el Reino de Jordania (...) Obama y Kerry deben dejar de criticar a Israel por los asentamientos. Judea y Samaria pertenecen a los israelíes»[^10]. En el programa de Wilders, «distinguiéndose durante dos décadas por su lucha contra la islamización —escribe complacido un sitio web sionista— está también el reconocimiento de Jerusalén como capital de Israel, con el traslado de la embajada holandesa»[^11]. André Ventura, presidente de *¡Chega!*, reiteró en Polonia la posición prosionista de su partido, declarando convencido: «Estamos con Israel y permaneceremos junto a Israel en esta batalla por los derechos humanos y la democracia»[^12]. A quienes lo comparan con Donald Trump y Jair Bolsonaro, André Ventura responde: «Estoy acostumbrado a estas comparaciones. Estas son las ideas en las que creo»[^13]. En cuanto a la guerra en Ucrania, el líder de la lista *¡Chega!* en las elecciones europeas, Antonio Tânger Corrêa, dijo que «la derrota de Ucrania sería la derrota de todo Occidente y de Portugal, en caso de extrema necesidad»[^14], enviarían a sus tropas. Marlene Svazek representó a la *Freiheitliche Partei Österreichs* en Pontida, cuyos «excelentes contactos»[^15] con la derecha israelí están garantizados por David Lasar, miembro del Consejo Nacional (*Nationalrat*) del partido austriaco. Lasar no es el único judío en el FPÖ: también es judío el ex-secretario general del partido y ex-parlamentario europeo Peter Sichrovsky, quien ha negado ser un agente del Mossad, pero ha admitido haber tenido «muchas reuniones con funcionarios israelís»[^16]. José Antonio Fúster es el nuevo presidente de *Vox* Madrid. El jefe del partido que lo representa, Santiago Abascal, encabezó una delegación a Israel en 2023 que se reunió con dos ministros de Tel Aviv. «Durante la visita, Abascal ha transmitido el apoyo y la solidaridad de España al Primer Ministro israelí Benjamin Netanyahu, y ha defendido la urgente necesidad de acabar con Hamas que, según Abascal, es un grupo terrorista que «encarna el mal absoluto»[^17]. Tras la reunión de la delegación de *Vox* con Netanyahu, el candidato electoral Jorge Buxadé Villalba afirmó que las acciones genocidas cometidas por el régimen sionista en la Franja de Gaza son «operaciones antiterroristas» que deben continuar «hasta que no quede ni un solo terrorista»[^18]. En cuanto a Roberto Vannacci, elegido diputado del Parlamento Europeo en las listas de la Liga por Salvini, su currículum vitae *patriot* puede jactarse de una participación activa en las operaciones de EE.UU. en Oriente Medio. El general comandó durante dos turnos (2005-2006) el *Special Forces Task Group* en Irak y fue el primer comandante de la *Task Force 45* en Afganistán en 2013, poco antes de la transición de la *International Security Assistance Force* a la *Resolute Support Mission*, Vannacci asumió el cargo de jefe del Estado Mayor de las fuerzas especiales de la OTAN, «una organización que ha garantizado la paz durante más de cincuenta años, una alianza política y militar que ha funcionado bien»[^19]. Habiendo prestado sus servicios a los Estados Unidos «para la estabilización de Irak»[^20] como *Deputy Commanding General* y *Director of Training*, el 21 de agosto de 2018, Vannacci fue galardonado con la *Legion of Merit*, la condecoración militar estadounidense creada por el presidente Franklin D. Roosevelt. Su consigna antes y después de la elección de Trump ha sido: «*Go, Donald, go!»*. [^1]: Cfr. C. Mutti, *Alla destra degli USA*, «Eurasia» 1/2023. [^2]: Después de la confluencia de los grupos de *Identity and Democracy* en el grupo de *Patriots*, se aprobó una nueva versión del manifiesto político. Véase [https://patriots.eu/manifesto](https://patriots.eu/manifesto) [^3]: Freiheitliche Partei Österreichs (Austria), 6; Vlaams Belang (Bélgica), 3; Dansk Folkeparti (Dinamarca), 1; Rassemblement National (Francia), 30; Foni Logikis (Grecia), 1; Fidesz - Magyar Polgári Szövetség (Hungría), 10; Kereszténydemokrata Néppárt (Hungría), 1; Liga para Salvini Premier (Italia), 8; Letvija primajâ vietâ (Letonia), 1; Partij voor de Vrijheid (Países Bajos), 6; Ruch Narodowy (Polonia), 2; ¡Chega! (Portugal), 2; ANO (República Checa), 7; Automovilistaé sobê (República Checa), 1; Přísaha (República Checa), 1; Vox (España), 6. [^4]: Angela Napoletano, *La «visita». Orbán incorona Trump: «Lui è il presidente della pace»*, avvenire.it, 9 marzo 2024. [^5]: András Dezsô, *The roots of Orbán’s strong bond with Israel and its PM*, [https://balkaninsight.com](https://balkaninsight.com), 14 de noviembre de 2023. [^6]: Bardella, «*riconoscere Palestina è riconoscere terrorismo*». «*Sarò uno scudo per i nostri connazionali ebrei*», ANSA, 26/6/2024. [^7]: Mauro Zanon, *Sorpresa, lo «scudo» degli ebrei in Francia è il partito della Le Pen*, [tempi.it](https://tempi.it/), 27 de octubre de 2023. [^8]: Stefano Baldolini, *Salvina punta su Trump: «Spero che vinca. Andrò negli Usa prima del voto». Tensioni con Meloni? «Governo durerà 5 anni»*, [repubblica.it](https://repubblica.it), 13 de julio de 2024. [^9]: Nova.News, 7 de octubre de 2024. [^10]: *Elezioni in Olanda, che è il sovranista Wilders: anti-Islam, contro l’Ue e sostenitore del Grande Israele*, [www.open.online](http://www.open.online), 23 de noviembre de 2023. [^11]: [www.informazionecorretta.com](http://www.informazionecorretta.com/), 26 de octubre de 2024. [^12]: [www.agenzianova.com](http://www.agenzianova.com), 6 de octubre de 2024. [^13]: *Especial: André Ventura. «Sou contra o aborto mas nunca condenaria uma mulher que aborta»*, «Jornal SOL», 12 de julio de 2022. [^14]: *Ventura admite tropas portuguesas na Ucrânia e tem uma posição clara sobre Putin*, «CNN Portugal», 11 de marzo de 2024. [^15]: Sophie Makris, *Austria’s Jews wary of far-right charm offensive*, [www.timeofisrael.com](http://www.timeofisrael.com), 3 de marzo de 2019. [^16]: Yossi Melman, *Sichrovsky Denies He Was a Mossad Agent*, [www.haaretz.com](http://www.haaretz.com), 3 de junio de 2005. [^17]: Fernando Heller, *Spagna: il leader di Vox pretende le scuse di Sánchez per aver messo in dubbio l’offensiva israeliana contro Hamas*, [https://euractiv.it](https://euractiv.it), 6 de diciembre de 2023. [^18]: *El ultraderechista Vox defiende los ataques de Israel en Gaza tras la polémica reunión con Netanyahu*, euronews, 29 de mayo de 2024. [^19]: Bruno Vespa, *Vannacci: «Dopo l’Ue tornerei nell’esercito»*, «La Verità», 30 de octubre de 2024, p. 7. [^20]: *Missione Iraq: Riconoscimento al Generale Roberto Vannacci,* en [www.difesa.it](http://www.difesa.it) , cit. en [www.wikipedia.org](http://www.wikipedia.org) --- **Artículo original**: Hipérbola Janus, [_Patriots_](https://www.hiperbolajanus.com/posts/patriots-mutti/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/patriots-mutti/), 9/Ene/2025
@ bcbb3e40:a494e501
2025-03-31 15:02:58Traducción por Francisco de la Torre. || |:-:| |Los representantes de la derecha sionista europea que forman parte de «Patriots» reunidos en Bruselas el pasado mes de diciembre de 2024.| Entre los efectos que probablemente producirá en Europa la nueva administración estadounidense, es previsible [el fortalecimiento del ala derecha del colaboracionismo atlantista](https://hiperbolajanus.com/posts/mos-maiorum-8/) que, después de haberse posicionado decididamente a favor de Donald Trump durante su presidencia 2017-2021, en el transcurso de la administración Biden abogó fervientemente por su regreso a la Casa Blanca y acogió su victoria electoral con gran júbilo. A finales de octubre de 2024, en el grandioso [mitin preelectoral a favor de Trump](https://hiperbolajanus.com/posts/adios-woke-que-viene-ahora/) celebrado en el Madison Square Garden de Nueva York, asistió una representante del grupo parlamentario europeo *Patriots for Europe*, que viajó a Estados Unidos para esa ocasión especial. En un vídeo publicado en la página X (antes twitter) de los *Patriots*, varios eurodiputados del mencionado grupo expresaron su identidad con los puntos de vista de Trump y auspiciando su reelección: el austriaco Harald Vilimsky (*Freiheitliche Partei Österreichs*), el checo Ondrej Knotek (*Año 2011*) el español Jorge Buxade (*Vox*), el holandés Tom Vandendriesche (*Vlaams Belang*), la polaca Anna Bryłka (*Ruch Narodowy*) y, por Hungría, Tamás Deutsch (*Fidesz*). Este último es, sin duda, la personalidad más eminente del grupo de los *Patriots* que viajaron a Nueva York: originario de una familia judía de Budapest, en 1988 Tamás Deutsch junto con Viktor Orbán están entre los fundadores de *Fidesz* —*Fiatal Demokraták Szövetsége* (Alianza de los jóvenes demócratas), en la que ocupó el cargo de vicepresidente. El *Fidesz* ha tejido durante mucho tiempo una red de lazos con el Partido Republicano de los Estados Unidos y con el think tank conservador *Heritage Foundation*, mientras que el gobierno de Viktor Orbán organizó las tres últimas ediciones anuales de la CPAC en Hungría (*Conservative Political Action Conference*), un encuentro de políticos de derechas de varios países[^1]. *Patriots for Europe* o *Patriots.eu*, denominación que recuerda al de los misiles aire-tierra estadounidenses (el *MIM-104 Patriots*), es, por tanto, el nombre oficial del grupo político de la derecha liberal-conservadora, populista y euroescéptica, nacido en julio de 2024 (primero como alianza y luego como grupo parlamentario europeo) por iniciativa del primer ministro húngaro Viktor Orbán, el exprimer ministro checo Andrej Babiŝ y del exministro del interior austriaco Herbert Kickl. Como representantes de sus respectivos partidos (*Fidesz*, *Año 2011*, *Freiheitliche Partei Österreichs*), Orbán, Babiŝ y Kickl firmaron un texto ideológico titulado: *A Patriotic Manifesto for a European Future*[^2], según la cual la única política europea legítima es aquella que, enraizada en la pluralidad de las diferentes naciones, proteja su herencia grecorromana-judeocristiana preservando su identidad, tradiciones y costumbres. Al núcleo inicial de los *Patriots* se unió el partido portugués *¡Arriva!* (*¡Chega!*), el Partido húngaro Popular Demócrata Cristiano (*Kereszténydemokrata Néppárt*), el partido español *Vox*, el Partido por la Libertad (*Partij voor de Vrijheid*) holandés, el Partido Popular Danés (*Dansk Folkeparti*), el interés Flamenco (*Vlaams Belang*), la Reunión Nacional (*Rassemblement National*) francés y, por Italia, la Liga para Primer Ministro Salvini. Constituido formalmente, el grupo parlamentario recibió una posterior adhesión del diputado griego de *Voz de la Razón* (*Foní Logikis*), del diputado de *Primero Letonia* (*Letvija pirmajâ prohibir*), de los dos diputados del Movimiento Nacional polaco (*Ruch Narodowy*) y de los dos diputados checos del Juramento (*Přísaha*) y de los Automovilistas por sí mismos (*Motoristé sollozoê*). Presidente del grupo parlamentario *Patriots.eu*, que cuenta con un total de ochenta y seis diputados[^3], es Jordan Bardella, presidente de la *Rassemblement National*; pero la personalidad más notable y prestigiosa de los *Patriots* es, sin duda, el primer ministro húngaro Viktor Orbán. En cuanto a la línea de política exterior seguida por Viktor Orbán, cabe recordar que fue durante su primer mandato, en 1989, cuando Hungría se unió a la OTAN junto con la República Checa y Polonia. La pertenencia a la organización militar de la Alianza Atlántica implicó la participación húngara en la guerra de Kosovo en Yugoslavia, así como la contribución de Hungría en las misiones de la ISAF y en la guerra en Irak en apoyo de la intervención estadounidense. Por otro lado, no deja de ser significativo que en junio de 2011, durante la visita de Condoleezza Rice a Budapest, se inaugurara una estatua del presidente estadounidense Ronald Reagan en la céntrica Plaza de la Libertad (*Szabadság tér*). «Hoy —dijo Orbán en esa ocasión— erigimos aquí una estatua al hombre, al líder, que cambió y renovó este mundo [creando un nuevo mundo para nosotros en Europa Central](https://hiperbolajanus.com/posts/presentacion-despues-virus-boris-nad/), un hombre que creía en la libertad, en la fuerza moral de los hombres libres, y creía que los muros que obstruyen el camino a la libertad pueden ser derribados». En los años de la primera administración Trump, Orbán estableció una relación privilegiada con la Casa Blanca: en 2019 fue recibido calurosamente por el presidente estadounidense, quien [declaró su apoyo al «soberanismo» europeo,](https://hiperbolajanus.com/libros/mos-maiorum-7/) del que Orbán era ya el exponente más puntero. El primer ministro húngaro, que más tarde expresó varias veces la esperanza de volver a ver a Trump como líder de los Estados Unidos, se reunió con él de nuevo en Mar-a-Lago de Palm Beach en marzo de 2024 y al final de la visita escribió en una publicación: «¡Hacer que América vuelva a ser grande, señor presidente!»[^4]. El entendimiento entre Trump y Orbán fue favorecido por Benjamin Netanyahu, quien ha tenido una estrecha relación con el actual primer ministro húngaro desde 2005, cuando Orbán estaba en la oposición y Netanyahu era ministro de Finanzas. Esta relación, que Orbán ha utilizado para neutralizar las iniciativas hostiles de las ONG’s de Soros (quien financió a *Fidesz* desde 1992 a 1999), ha acentuado progresivamente la posición proisraelí de Budapest, hasta el punto que Hungría junto a Austria, Croacia y República Checa, se han alineado con Estados Unidos e Israel votando en contra de la resolución propuesta por la ONU para el alto el fuego en la Franja de Gaza. Cuando László Toroczkai, jefe del partido *Mi Hazánk* (Nuestra Patria), preguntó a Orbán en el Parlamento por qué Hungría había votado en contra, el primer ministro le respondió: «La política exterior es complicada, enfréntate solo si entiendes de lo que estamos hablando»[^5]. El presidente de *Patriots*, Jordan Bardella, no es menos pro-sionista. «Reconocer un Estado palestino significaría reconocer el terrorismo», dijo Bardella, quien antes de las elecciones francesas había asegurado que, si llegaba a ser primer ministro, sería «un escudo para los compatriotas judíos contra un islamismo que no solo quiere separar la República, sino conquistarla»[^6]. Por su parte, Marine Le Pen, madrina política de Bardella, declaró: «Es absolutamente legítimo que Israel quiera erradicar al grupo terrorista armado Hamas y que se dote de medios para hacerlo»[^7]. En cuanto a la Liga de Salvini como primer ministro, sus posiciones pro-trumpistas y pro-sionistas siempre se han caracterizado por un extremismo descarado. «Nunca he ocultado —dijo Salvini antes de las elecciones estadounidenses— mi esperanza en una victoria republicana, por mil razones (...) hablamos [con Trump] a más tardar hace unas semanas. Nunca he ocultado mi simpatía humana y mi sintonía cultural»[^8]. Y sobre el genocidio en curso en Palestina, Salvini dijo: «Nuestros pensamientos están con el pueblo israelí (...) Recordar siempre el derecho de Israel a existir, a defenderse y a convivir finalmente en paz con sus pueblos vecinos, contra el horror del terrorismo islámico»[^9]. El 6 de octubre de 2024, al final de su discurso desde el escenario de Pontida, Salvini posó para una foto con los *Patriots* presentes en la manifestación de la Liga Norte: además de Viktor Orbán, estuvieron el holandés Geert Wilders, el portugués André Ventura, la austriaca Marlene Svazek, el español Antonio Fúster y el general Roberto Vannacci. Enviaron mensajes en vídeo de apoyo y solidaridad tanto Jordán Bardella en nombre de *Rassemblement national* como el ex-presidente brasileño Jair Bolsonaro. También Geert Wilders (*Partij voor de Vrijheid*), que en 2009 recibió el Premio Oriana Fallaci por producir un cortometraje de propaganda antiislámica, es conocido también por su extremismo prosionista. «Jerusalén, Judea y Samaria —en su opinión— son todas de Israel (...) La patria de los palestinos es el Reino de Jordania (...) Obama y Kerry deben dejar de criticar a Israel por los asentamientos. Judea y Samaria pertenecen a los israelíes»[^10]. En el programa de Wilders, «distinguiéndose durante dos décadas por su lucha contra la islamización —escribe complacido un sitio web sionista— está también el reconocimiento de Jerusalén como capital de Israel, con el traslado de la embajada holandesa»[^11]. André Ventura, presidente de *¡Chega!*, reiteró en Polonia la posición prosionista de su partido, declarando convencido: «Estamos con Israel y permaneceremos junto a Israel en esta batalla por los derechos humanos y la democracia»[^12]. A quienes lo comparan con Donald Trump y Jair Bolsonaro, André Ventura responde: «Estoy acostumbrado a estas comparaciones. Estas son las ideas en las que creo»[^13]. En cuanto a la guerra en Ucrania, el líder de la lista *¡Chega!* en las elecciones europeas, Antonio Tânger Corrêa, dijo que «la derrota de Ucrania sería la derrota de todo Occidente y de Portugal, en caso de extrema necesidad»[^14], enviarían a sus tropas. Marlene Svazek representó a la *Freiheitliche Partei Österreichs* en Pontida, cuyos «excelentes contactos»[^15] con la derecha israelí están garantizados por David Lasar, miembro del Consejo Nacional (*Nationalrat*) del partido austriaco. Lasar no es el único judío en el FPÖ: también es judío el ex-secretario general del partido y ex-parlamentario europeo Peter Sichrovsky, quien ha negado ser un agente del Mossad, pero ha admitido haber tenido «muchas reuniones con funcionarios israelís»[^16]. José Antonio Fúster es el nuevo presidente de *Vox* Madrid. El jefe del partido que lo representa, Santiago Abascal, encabezó una delegación a Israel en 2023 que se reunió con dos ministros de Tel Aviv. «Durante la visita, Abascal ha transmitido el apoyo y la solidaridad de España al Primer Ministro israelí Benjamin Netanyahu, y ha defendido la urgente necesidad de acabar con Hamas que, según Abascal, es un grupo terrorista que «encarna el mal absoluto»[^17]. Tras la reunión de la delegación de *Vox* con Netanyahu, el candidato electoral Jorge Buxadé Villalba afirmó que las acciones genocidas cometidas por el régimen sionista en la Franja de Gaza son «operaciones antiterroristas» que deben continuar «hasta que no quede ni un solo terrorista»[^18]. En cuanto a Roberto Vannacci, elegido diputado del Parlamento Europeo en las listas de la Liga por Salvini, su currículum vitae *patriot* puede jactarse de una participación activa en las operaciones de EE.UU. en Oriente Medio. El general comandó durante dos turnos (2005-2006) el *Special Forces Task Group* en Irak y fue el primer comandante de la *Task Force 45* en Afganistán en 2013, poco antes de la transición de la *International Security Assistance Force* a la *Resolute Support Mission*, Vannacci asumió el cargo de jefe del Estado Mayor de las fuerzas especiales de la OTAN, «una organización que ha garantizado la paz durante más de cincuenta años, una alianza política y militar que ha funcionado bien»[^19]. Habiendo prestado sus servicios a los Estados Unidos «para la estabilización de Irak»[^20] como *Deputy Commanding General* y *Director of Training*, el 21 de agosto de 2018, Vannacci fue galardonado con la *Legion of Merit*, la condecoración militar estadounidense creada por el presidente Franklin D. Roosevelt. Su consigna antes y después de la elección de Trump ha sido: «*Go, Donald, go!»*. [^1]: Cfr. C. Mutti, *Alla destra degli USA*, «Eurasia» 1/2023. [^2]: Después de la confluencia de los grupos de *Identity and Democracy* en el grupo de *Patriots*, se aprobó una nueva versión del manifiesto político. Véase [https://patriots.eu/manifesto](https://patriots.eu/manifesto) [^3]: Freiheitliche Partei Österreichs (Austria), 6; Vlaams Belang (Bélgica), 3; Dansk Folkeparti (Dinamarca), 1; Rassemblement National (Francia), 30; Foni Logikis (Grecia), 1; Fidesz - Magyar Polgári Szövetség (Hungría), 10; Kereszténydemokrata Néppárt (Hungría), 1; Liga para Salvini Premier (Italia), 8; Letvija primajâ vietâ (Letonia), 1; Partij voor de Vrijheid (Países Bajos), 6; Ruch Narodowy (Polonia), 2; ¡Chega! (Portugal), 2; ANO (República Checa), 7; Automovilistaé sobê (República Checa), 1; Přísaha (República Checa), 1; Vox (España), 6. [^4]: Angela Napoletano, *La «visita». Orbán incorona Trump: «Lui è il presidente della pace»*, avvenire.it, 9 marzo 2024. [^5]: András Dezsô, *The roots of Orbán’s strong bond with Israel and its PM*, [https://balkaninsight.com](https://balkaninsight.com), 14 de noviembre de 2023. [^6]: Bardella, «*riconoscere Palestina è riconoscere terrorismo*». «*Sarò uno scudo per i nostri connazionali ebrei*», ANSA, 26/6/2024. [^7]: Mauro Zanon, *Sorpresa, lo «scudo» degli ebrei in Francia è il partito della Le Pen*, [tempi.it](https://tempi.it/), 27 de octubre de 2023. [^8]: Stefano Baldolini, *Salvina punta su Trump: «Spero che vinca. Andrò negli Usa prima del voto». Tensioni con Meloni? «Governo durerà 5 anni»*, [repubblica.it](https://repubblica.it), 13 de julio de 2024. [^9]: Nova.News, 7 de octubre de 2024. [^10]: *Elezioni in Olanda, che è il sovranista Wilders: anti-Islam, contro l’Ue e sostenitore del Grande Israele*, [www.open.online](http://www.open.online), 23 de noviembre de 2023. [^11]: [www.informazionecorretta.com](http://www.informazionecorretta.com/), 26 de octubre de 2024. [^12]: [www.agenzianova.com](http://www.agenzianova.com), 6 de octubre de 2024. [^13]: *Especial: André Ventura. «Sou contra o aborto mas nunca condenaria uma mulher que aborta»*, «Jornal SOL», 12 de julio de 2022. [^14]: *Ventura admite tropas portuguesas na Ucrânia e tem uma posição clara sobre Putin*, «CNN Portugal», 11 de marzo de 2024. [^15]: Sophie Makris, *Austria’s Jews wary of far-right charm offensive*, [www.timeofisrael.com](http://www.timeofisrael.com), 3 de marzo de 2019. [^16]: Yossi Melman, *Sichrovsky Denies He Was a Mossad Agent*, [www.haaretz.com](http://www.haaretz.com), 3 de junio de 2005. [^17]: Fernando Heller, *Spagna: il leader di Vox pretende le scuse di Sánchez per aver messo in dubbio l’offensiva israeliana contro Hamas*, [https://euractiv.it](https://euractiv.it), 6 de diciembre de 2023. [^18]: *El ultraderechista Vox defiende los ataques de Israel en Gaza tras la polémica reunión con Netanyahu*, euronews, 29 de mayo de 2024. [^19]: Bruno Vespa, *Vannacci: «Dopo l’Ue tornerei nell’esercito»*, «La Verità», 30 de octubre de 2024, p. 7. [^20]: *Missione Iraq: Riconoscimento al Generale Roberto Vannacci,* en [www.difesa.it](http://www.difesa.it) , cit. en [www.wikipedia.org](http://www.wikipedia.org) --- **Artículo original**: Hipérbola Janus, [_Patriots_](https://www.hiperbolajanus.com/posts/patriots-mutti/) [**(TOR)**](http://hiperbolam7t46pbl2fiqzaarcmw6injdru4nh2pwuhrkoub3263mpad.onion/posts/patriots-mutti/), 9/Ene/2025 @ fe02e8ec:f07fbe0b
2025-03-31 14:43:22\ Und genau dafür wirst auch du gedrillt werden: Menschen zu jagen und töten. Unbekannte, die auch nicht wissen, was sie hier tun. Oder Unschuldige, die nicht rechtzeitig fliehen konnten. Einfach töten. Alle. Ohne zu fragen. Denn das ist deine Aufgabe, Soldat: **Töte Menschen!** Egal, was du vorher warst, Heizungsmonteur, KFZ-Mechaniker, Veganer, Marketing-Manager, Friseur, Verkäufer, Kindergärtner: Es ist egal. Jetzt musst du töten. Denn du hast mitgemacht. Entweder, weil du es nicht ernst genommen hast, weil du dich nie für Politik interessiert hast. Oder weil du gedacht hast, das alles betrifft dich nicht. Weil du gedacht hast, Wahlen könnten etwas verändern. Oder weil du immer das Maul gehalten hast, damit dich keiner als «Rechter» bezeichnet. Egal. Jetzt musst du töten. Das ist das Spiel. Ja, es ist ein Spiel. Grausam, abartig, menschenverachtend. Dennoch hat es Regeln: Diejenigen, die das Spiel beginnen, müssen niemals selbst auf das Schlachtfeld. Das ist die erste Regel. Ihre Söhne auch nicht, nicht die Söhne der anderen Politiker, nicht die der EU-Abgeordneten, nicht die der Parteibonzen. Auch nicht die der Banker, der Vorstandsvorsitzenden, der Chefredakteure. Denn alle wissen, wie man das Spiel spielt. Nur du nicht. Du bist einfach eine Figur auf dem Spielfeld, die es verpasst hat, **NEIN zu sagen, als noch Gelegenheit war.** Jetzt bist du verwandelt worden in eine menschliche Drohne. Wenn sie sagen: töte!, dann tötest du. Denken kannst du, wenn alles vorbei ist. Falls du je wieder nach Hause kommst. Vielleicht sogar mit beiden Beinen und beiden Armen. Vielleicht auch nicht. Egal. Wer hätte Mitleid mit einer Spielfigur? Nein, du musst töten. Das ist deine Aufgabe. Sie sagen es nun schon seit Monaten, warum glaubst du es nicht? Sie meinen es ernst. Wenn du den Brief in Händen hältst ist es zu spät. Es gilt dann das Notstandsrecht und keiner kann mehr verweigern. Da hättest du dich vorher drum kümmern müssen. Oder auf eine Demo gehen. Oder laut und mit klarer Stimme in jedem Gespräch den Wahnsinn anprangern. Hast du aber nicht. **Jetzt musst du töten oder du wirst getötet.** Das ist das Spiel. Du hättest selbst denken können. Hast du aber nicht. Hast deine Zeit mit sinnlosen Videos vertan, Netflix geguckt und hast Influencerinnen geliked. Die müssen nicht an die Front. Aber du. Morgen, wenn du aufstehst, die Uniform anziehst und rausgehst, dann wirst du Befehle ausführen oder erschossen werden. Also wirst du Menschen töten. Dein Leben wird nie wieder so sein, wie zuvor. **Dein Schmerz, deine Schuld, dein Leid**: sie gehen ein in die unendliche Reihe der Soldaten, die seit Jahrhunderten dasselbe Schicksal erlitten. Deren Schreie noch immer durch den ewigen Raum hallen. Deren Opfer von den Herren des Spiels mit einem Lächeln entgegengenommen wurde. Deren Gliedmaßen auf den Schlachtfeldern liegen geblieben waren. Zum Dank erhielten sie eine Medaille. Ein Stück Blech für den rechten Arm, einen Grabstein für den Vater, den Bruder, den Sohn. Für das Vaterland. Für Europa. Für die Demokratie. Der Hohn tropft aus jedem Politikerwort, doch **die Menschen glauben noch immer die uralte Geschichte von Freund und Feind, von Gut und Böse**. ") \ **Wer nicht aufwachen will muss töten.** Du. Nicht am Bildschirm. In der echten Welt. Wo man nicht auf Replay drücken kann. Wo man den Gegner nicht nach links oder rechts swipen kann, denn er ist echt, real, lebendig. Noch. Entweder er oder du. Jetzt ist es zu spät für Entscheidungen. Kannst du es spüren? Die Work-Life Balance wird zur Kill-or-be-Killed balance. Es gibt kein Entrinnen. Denn du hast mitgemacht. Schweigen ist Zustimmung. Sich-nicht-drumkümmern ist Zustimmung. Kriegsparteien zu wählen ist noch mehr Zustimmung. **Heute.** **Heute lässt sich noch etwas ändern.** Es hat nichts zu tun mit rechts oder links. Nur mit Menschlichkeit versus Hass, Macht und dem ganz großen Geld. Das sind die Gründe, für die du töten oder sterben musst. **Wie entscheidest du dich?**
@ fe02e8ec:f07fbe0b
2025-03-31 14:43:22\ Und genau dafür wirst auch du gedrillt werden: Menschen zu jagen und töten. Unbekannte, die auch nicht wissen, was sie hier tun. Oder Unschuldige, die nicht rechtzeitig fliehen konnten. Einfach töten. Alle. Ohne zu fragen. Denn das ist deine Aufgabe, Soldat: **Töte Menschen!** Egal, was du vorher warst, Heizungsmonteur, KFZ-Mechaniker, Veganer, Marketing-Manager, Friseur, Verkäufer, Kindergärtner: Es ist egal. Jetzt musst du töten. Denn du hast mitgemacht. Entweder, weil du es nicht ernst genommen hast, weil du dich nie für Politik interessiert hast. Oder weil du gedacht hast, das alles betrifft dich nicht. Weil du gedacht hast, Wahlen könnten etwas verändern. Oder weil du immer das Maul gehalten hast, damit dich keiner als «Rechter» bezeichnet. Egal. Jetzt musst du töten. Das ist das Spiel. Ja, es ist ein Spiel. Grausam, abartig, menschenverachtend. Dennoch hat es Regeln: Diejenigen, die das Spiel beginnen, müssen niemals selbst auf das Schlachtfeld. Das ist die erste Regel. Ihre Söhne auch nicht, nicht die Söhne der anderen Politiker, nicht die der EU-Abgeordneten, nicht die der Parteibonzen. Auch nicht die der Banker, der Vorstandsvorsitzenden, der Chefredakteure. Denn alle wissen, wie man das Spiel spielt. Nur du nicht. Du bist einfach eine Figur auf dem Spielfeld, die es verpasst hat, **NEIN zu sagen, als noch Gelegenheit war.** Jetzt bist du verwandelt worden in eine menschliche Drohne. Wenn sie sagen: töte!, dann tötest du. Denken kannst du, wenn alles vorbei ist. Falls du je wieder nach Hause kommst. Vielleicht sogar mit beiden Beinen und beiden Armen. Vielleicht auch nicht. Egal. Wer hätte Mitleid mit einer Spielfigur? Nein, du musst töten. Das ist deine Aufgabe. Sie sagen es nun schon seit Monaten, warum glaubst du es nicht? Sie meinen es ernst. Wenn du den Brief in Händen hältst ist es zu spät. Es gilt dann das Notstandsrecht und keiner kann mehr verweigern. Da hättest du dich vorher drum kümmern müssen. Oder auf eine Demo gehen. Oder laut und mit klarer Stimme in jedem Gespräch den Wahnsinn anprangern. Hast du aber nicht. **Jetzt musst du töten oder du wirst getötet.** Das ist das Spiel. Du hättest selbst denken können. Hast du aber nicht. Hast deine Zeit mit sinnlosen Videos vertan, Netflix geguckt und hast Influencerinnen geliked. Die müssen nicht an die Front. Aber du. Morgen, wenn du aufstehst, die Uniform anziehst und rausgehst, dann wirst du Befehle ausführen oder erschossen werden. Also wirst du Menschen töten. Dein Leben wird nie wieder so sein, wie zuvor. **Dein Schmerz, deine Schuld, dein Leid**: sie gehen ein in die unendliche Reihe der Soldaten, die seit Jahrhunderten dasselbe Schicksal erlitten. Deren Schreie noch immer durch den ewigen Raum hallen. Deren Opfer von den Herren des Spiels mit einem Lächeln entgegengenommen wurde. Deren Gliedmaßen auf den Schlachtfeldern liegen geblieben waren. Zum Dank erhielten sie eine Medaille. Ein Stück Blech für den rechten Arm, einen Grabstein für den Vater, den Bruder, den Sohn. Für das Vaterland. Für Europa. Für die Demokratie. Der Hohn tropft aus jedem Politikerwort, doch **die Menschen glauben noch immer die uralte Geschichte von Freund und Feind, von Gut und Böse**. ") \ **Wer nicht aufwachen will muss töten.** Du. Nicht am Bildschirm. In der echten Welt. Wo man nicht auf Replay drücken kann. Wo man den Gegner nicht nach links oder rechts swipen kann, denn er ist echt, real, lebendig. Noch. Entweder er oder du. Jetzt ist es zu spät für Entscheidungen. Kannst du es spüren? Die Work-Life Balance wird zur Kill-or-be-Killed balance. Es gibt kein Entrinnen. Denn du hast mitgemacht. Schweigen ist Zustimmung. Sich-nicht-drumkümmern ist Zustimmung. Kriegsparteien zu wählen ist noch mehr Zustimmung. **Heute.** **Heute lässt sich noch etwas ändern.** Es hat nichts zu tun mit rechts oder links. Nur mit Menschlichkeit versus Hass, Macht und dem ganz großen Geld. Das sind die Gründe, für die du töten oder sterben musst. **Wie entscheidest du dich?** @ 0d1702d6:8f1ac66f
2025-03-31 10:45:57*Als Verrücktheit bezeichnen* \ *wir die chronische Entwicklung* \ *eines dauernden Wahnsystems* \ *bei vollkommener Erhaltung* \ *der Besonnenheit.* **Psychiater Emil Kraepelin 1893** Es ist **Teil des westlichen Wahnsystems** anzunehmen, Russland habe aus imperialen Absichten heraus 2022 mit nur 130.000 Soldaten die Grenze zur Ukraine überschritten, um so die gesamte Ukraine und später wohlmöglich Westeuropa militärisch einzunehmen, wie z.B. der deutsche Kriegsminister Pistorius seit 2023 suggerierte. Nachdem die USA bereits 2014 die berechtigten Anti-Korruptions-Proteste der Ukrainer auf dem Maidan durch massive Unterstützung für einen illegalen Putsch gegen die russlandfreundliche Regierung im Sinne des von den USA gewünschten Regimewechsels manipuliert hatten, rüsteten sie in den folgenden Jahren die Ukraine massiv auf, trainierten ihre Soldaten, bauten mehr als einen Stützpunkt und machten die zwischen Ost & West hin- und hergerissene Ukraine so zielgerichtet unterhalb offizieller NATO-Mitgliedschaft schon zu einem kampfstarken eng befreundeten Partner, dessen Krieg gegen seine eigene russisch-stämmige Bevölkerung im rohstoffreichen Donbass die NATO unter Führung der USA somit auch direkt und indirekt unterstützte. Nachdem der Westen den Russen bei der Wiedervereinigung Deutschlands versprochen hatte, die NATO keinen Zentimeter nach Osten vorzuschieben und stattdessen ein gemeinsames europäisches Sicherheits-System unter Einbeziehung Russlands gemeinsam zu entwickeln, brachen wir diese Zusicherung mit den NATO-Osterweiterungen ab 1999 mehrfach bis heute. Russland zeigte sich bei seiner zunehmenden Umzingelung durch NATO-Staaten wesentlich nachsichtiger als es umgekehrt die USA schon bei russischen wenigen Raketen auf Kuba 1962 jemals waren und heute sein würden! Zugleich hatte Russland seit Beginn der NATO-Osterweiterung immer unmissverständlich klar gemacht, dass es eine Stationierung von NATO-Truppen & Raketen in der Ukraine niemals tolerieren würde. Der damalige US-Senator und 2022 US-Präsident Biden sagte schon Ende der 90'er Jahre öffentlich, man werde auf diesen Wunsch der – nach Meinung von US-Geostrategen viel zu schwächen – Russen keine Rücksicht nehmen und erwarte, dass ihnen irgendwann die Nerven ob dieser provokativen Umzingelung durchgingen… Folgerichtig simulierten die USA und die Europäer - wie Angela Merkel bereits öffentlich eingestanden - nur Verhandlungen über die Abkommen Minsk I und II, damit genügend Zeit blieb die Ukraine aufzurüsten und diese dann einen starken militärischen Schlag gegen die russisch stämmige Bevölkerung im Donbass und die russischen Soldaten auf der Krim ausführen konnte, ein Szenario, welches Anfang 2022 durch einen Truppenaufmarsch auch auf ukrainischer Seite weit fortgeschritten vorbereitet war, bevor im Februar 2022 die russische Armee die Grenze zur Ukraine überschritt.\ \ Trotz alledem kamen schon im April 2022 Unterhändler der Ukraine und Russlands in Ankara zur Übereinkunft eines Waffenstillstandes und Friedensplans (!), der dann allerdings von dem damaligen britischen Premierminister Boris Johnson – in Kooperation mit Joe Biden – durch einen Besuch in Kiew mit dem Versprechen von grenzenlosen Waffenlieferungen \ & logistischer Unterstützung durch die USA und Westeuropa „abgetrieben“ wurde.\ \ Zunächst wurden diese Tatsachen wie üblich öffentlich in deutschen und europäischen Medien als „Verschwörungstheorie“ diffamiert, bis sie in den folgenden Monaten jedoch langsam selbst in die Mainstream-Medien Deutschlands, Europas wie den USA einsickerten.\ \ **Zwischenfazit:**\ Nachdem die USA ihre so und so viel gewählte globale „Regime Change“ Operation auf dem Maidan schon 10 Jahre lang vorbereitet hatten, gelang ihnen im Jahr 2014 tatsächlich zunächst einen pro-westlichen illegalen Putschpräsidenten, danach auch weitere pro-westliche Präsidenten zu installieren und einem Teil der Weltöffentlichkeit, vor allem aber ihren „Freunden“ im Westen einzureden, die „bösen Russen“ hätten diesen Krieg quasi aus dem Nichts heraus (ohne lange Vorgeschichte!) und trotz Verhandlungen (welche realen statt nur simulierten Verhandlungen?) vom Zaun gebrochen...\ \ Damit war ihr seit über 30 Jahren offen formuliertes geostrategisches Kalkül, \ die Schwäche der Russen nach Auflösung des Warschauer Paktes auszunutzen, sie mit der NATO zu umzingeln und bei Widerstand dann eben in einem kräftezehrenden Krieg stark zu schwächen und damit ein für alle Male als ökonomische Konkurrenten in Europa auszuschalten scheinbar aufgegangen...\ \ Das paranoide alte und zugleich kindliche „Freund/Feind Schema“ hatte seinen Dienst verrichtet und das „imperiale Böse“ konnte bequem auf „Putin und die Russen“ projiziert werden.  \ **Schizophren** ist dies auch deswegen, weil mit zweierlei Maß gemessen wurde und wird, denn niemals würden die USA auch nur eine russische Rakete auf Kuba tolerieren und gehen selber - ganz anders als Russland - global weit über die eigene Grenzsicherung hinaus, indem sie sich anmaßen, den gesamten Globus mit fast 800 Militärbasen zu überziehen und je nach Bedarf Kriege zu führen, wenn es ihnen zur Sicherung ihrer Rohstoffe - für auch unseren westlichen Lebensstil - und/oder geostrategischen Macht opportun und machbar erscheint.\ \ Deutschland spielt seit 2022 die naive und mehr als traurige Vorreiterrolle eines unterwürfigen Vasallen der so tut, als würde unsere Freiheit durch gegenseitigen Mord und Totschlag von Hunderttausenden junger Ukrainer und Russen in der Ukraine verteidigt, eine äußerst perverse und dümmliche Vorstellung ohne historische geschweige denn geo-strategische Kenntnisse und Erfahrungswerte.\ \ Demgegenüber ist klar: Es gibt nur EINE Sicherheit in Europa für alle vom Atlantik bis hinter den Ural, oder es gibt KEINE Sicherheit für Niemanden, \ wenn wir nicht die berechtigten Sicherheitsinteressen der Russen ernst nehmen, die wir, d.h. die unsere Väter und Großväter bereits im 20.Jahrhundert rücksichtslos überfallen, mit Krieg überzogen und ermordet haben.\ \ John F. Kennedy und Nikita S. Chruschtschow waren 1962 im historischen Gegenstück zum „Ukrainekrieg“, der „Kubakrise“, weise genug einen Weltkrieg durch gegenseitige Zugeständnisse zu verhindern. **Wo sind die Politiker von Format, die in ihre Fußstapfen treten?**\ \ Es wäre eine bitterböse Farce, wenn ausgerechnet ein autoritärer Oligarchen-Präsident wie Donald Trump die Weisheit hätte, diesen Schritt zu tun...\ \ Zugleich wäre die öffentliche Bankrott-Erklärung aller europäischen Politiker, \ die sich als viel demokratischer, sachlicher und menschlicher ansehen \ und ihre eigene dramatische Fehlleistung wohl niemals eingestehen...\ \ Allein die politische wie mediale Empörungswelle in Deutschland, als Trump und Putin ganz offenlegten, wer denn in diesem Krieg das Sagen hat, \ lässt Schlimmstes befürchten. Obwohl aus gut unterrichteten Diplomatenkreisen längst durchgesickert ist, dass im Prinzip die gesamte Analyse hier unter Diplomaten anerkannt und ziemlich nah an den Tatsachen ist, gehört nicht viel Lebenserfahrung dazu zu wissen, dass die meisten der ach so mächtigen westeuropäischen Politiker dies nie zugeben werden...
@ 0d1702d6:8f1ac66f
2025-03-31 10:45:57*Als Verrücktheit bezeichnen* \ *wir die chronische Entwicklung* \ *eines dauernden Wahnsystems* \ *bei vollkommener Erhaltung* \ *der Besonnenheit.* **Psychiater Emil Kraepelin 1893** Es ist **Teil des westlichen Wahnsystems** anzunehmen, Russland habe aus imperialen Absichten heraus 2022 mit nur 130.000 Soldaten die Grenze zur Ukraine überschritten, um so die gesamte Ukraine und später wohlmöglich Westeuropa militärisch einzunehmen, wie z.B. der deutsche Kriegsminister Pistorius seit 2023 suggerierte. Nachdem die USA bereits 2014 die berechtigten Anti-Korruptions-Proteste der Ukrainer auf dem Maidan durch massive Unterstützung für einen illegalen Putsch gegen die russlandfreundliche Regierung im Sinne des von den USA gewünschten Regimewechsels manipuliert hatten, rüsteten sie in den folgenden Jahren die Ukraine massiv auf, trainierten ihre Soldaten, bauten mehr als einen Stützpunkt und machten die zwischen Ost & West hin- und hergerissene Ukraine so zielgerichtet unterhalb offizieller NATO-Mitgliedschaft schon zu einem kampfstarken eng befreundeten Partner, dessen Krieg gegen seine eigene russisch-stämmige Bevölkerung im rohstoffreichen Donbass die NATO unter Führung der USA somit auch direkt und indirekt unterstützte. Nachdem der Westen den Russen bei der Wiedervereinigung Deutschlands versprochen hatte, die NATO keinen Zentimeter nach Osten vorzuschieben und stattdessen ein gemeinsames europäisches Sicherheits-System unter Einbeziehung Russlands gemeinsam zu entwickeln, brachen wir diese Zusicherung mit den NATO-Osterweiterungen ab 1999 mehrfach bis heute. Russland zeigte sich bei seiner zunehmenden Umzingelung durch NATO-Staaten wesentlich nachsichtiger als es umgekehrt die USA schon bei russischen wenigen Raketen auf Kuba 1962 jemals waren und heute sein würden! Zugleich hatte Russland seit Beginn der NATO-Osterweiterung immer unmissverständlich klar gemacht, dass es eine Stationierung von NATO-Truppen & Raketen in der Ukraine niemals tolerieren würde. Der damalige US-Senator und 2022 US-Präsident Biden sagte schon Ende der 90'er Jahre öffentlich, man werde auf diesen Wunsch der – nach Meinung von US-Geostrategen viel zu schwächen – Russen keine Rücksicht nehmen und erwarte, dass ihnen irgendwann die Nerven ob dieser provokativen Umzingelung durchgingen… Folgerichtig simulierten die USA und die Europäer - wie Angela Merkel bereits öffentlich eingestanden - nur Verhandlungen über die Abkommen Minsk I und II, damit genügend Zeit blieb die Ukraine aufzurüsten und diese dann einen starken militärischen Schlag gegen die russisch stämmige Bevölkerung im Donbass und die russischen Soldaten auf der Krim ausführen konnte, ein Szenario, welches Anfang 2022 durch einen Truppenaufmarsch auch auf ukrainischer Seite weit fortgeschritten vorbereitet war, bevor im Februar 2022 die russische Armee die Grenze zur Ukraine überschritt.\ \ Trotz alledem kamen schon im April 2022 Unterhändler der Ukraine und Russlands in Ankara zur Übereinkunft eines Waffenstillstandes und Friedensplans (!), der dann allerdings von dem damaligen britischen Premierminister Boris Johnson – in Kooperation mit Joe Biden – durch einen Besuch in Kiew mit dem Versprechen von grenzenlosen Waffenlieferungen \ & logistischer Unterstützung durch die USA und Westeuropa „abgetrieben“ wurde.\ \ Zunächst wurden diese Tatsachen wie üblich öffentlich in deutschen und europäischen Medien als „Verschwörungstheorie“ diffamiert, bis sie in den folgenden Monaten jedoch langsam selbst in die Mainstream-Medien Deutschlands, Europas wie den USA einsickerten.\ \ **Zwischenfazit:**\ Nachdem die USA ihre so und so viel gewählte globale „Regime Change“ Operation auf dem Maidan schon 10 Jahre lang vorbereitet hatten, gelang ihnen im Jahr 2014 tatsächlich zunächst einen pro-westlichen illegalen Putschpräsidenten, danach auch weitere pro-westliche Präsidenten zu installieren und einem Teil der Weltöffentlichkeit, vor allem aber ihren „Freunden“ im Westen einzureden, die „bösen Russen“ hätten diesen Krieg quasi aus dem Nichts heraus (ohne lange Vorgeschichte!) und trotz Verhandlungen (welche realen statt nur simulierten Verhandlungen?) vom Zaun gebrochen...\ \ Damit war ihr seit über 30 Jahren offen formuliertes geostrategisches Kalkül, \ die Schwäche der Russen nach Auflösung des Warschauer Paktes auszunutzen, sie mit der NATO zu umzingeln und bei Widerstand dann eben in einem kräftezehrenden Krieg stark zu schwächen und damit ein für alle Male als ökonomische Konkurrenten in Europa auszuschalten scheinbar aufgegangen...\ \ Das paranoide alte und zugleich kindliche „Freund/Feind Schema“ hatte seinen Dienst verrichtet und das „imperiale Böse“ konnte bequem auf „Putin und die Russen“ projiziert werden.  \ **Schizophren** ist dies auch deswegen, weil mit zweierlei Maß gemessen wurde und wird, denn niemals würden die USA auch nur eine russische Rakete auf Kuba tolerieren und gehen selber - ganz anders als Russland - global weit über die eigene Grenzsicherung hinaus, indem sie sich anmaßen, den gesamten Globus mit fast 800 Militärbasen zu überziehen und je nach Bedarf Kriege zu führen, wenn es ihnen zur Sicherung ihrer Rohstoffe - für auch unseren westlichen Lebensstil - und/oder geostrategischen Macht opportun und machbar erscheint.\ \ Deutschland spielt seit 2022 die naive und mehr als traurige Vorreiterrolle eines unterwürfigen Vasallen der so tut, als würde unsere Freiheit durch gegenseitigen Mord und Totschlag von Hunderttausenden junger Ukrainer und Russen in der Ukraine verteidigt, eine äußerst perverse und dümmliche Vorstellung ohne historische geschweige denn geo-strategische Kenntnisse und Erfahrungswerte.\ \ Demgegenüber ist klar: Es gibt nur EINE Sicherheit in Europa für alle vom Atlantik bis hinter den Ural, oder es gibt KEINE Sicherheit für Niemanden, \ wenn wir nicht die berechtigten Sicherheitsinteressen der Russen ernst nehmen, die wir, d.h. die unsere Väter und Großväter bereits im 20.Jahrhundert rücksichtslos überfallen, mit Krieg überzogen und ermordet haben.\ \ John F. Kennedy und Nikita S. Chruschtschow waren 1962 im historischen Gegenstück zum „Ukrainekrieg“, der „Kubakrise“, weise genug einen Weltkrieg durch gegenseitige Zugeständnisse zu verhindern. **Wo sind die Politiker von Format, die in ihre Fußstapfen treten?**\ \ Es wäre eine bitterböse Farce, wenn ausgerechnet ein autoritärer Oligarchen-Präsident wie Donald Trump die Weisheit hätte, diesen Schritt zu tun...\ \ Zugleich wäre die öffentliche Bankrott-Erklärung aller europäischen Politiker, \ die sich als viel demokratischer, sachlicher und menschlicher ansehen \ und ihre eigene dramatische Fehlleistung wohl niemals eingestehen...\ \ Allein die politische wie mediale Empörungswelle in Deutschland, als Trump und Putin ganz offenlegten, wer denn in diesem Krieg das Sagen hat, \ lässt Schlimmstes befürchten. Obwohl aus gut unterrichteten Diplomatenkreisen längst durchgesickert ist, dass im Prinzip die gesamte Analyse hier unter Diplomaten anerkannt und ziemlich nah an den Tatsachen ist, gehört nicht viel Lebenserfahrung dazu zu wissen, dass die meisten der ach so mächtigen westeuropäischen Politiker dies nie zugeben werden... @ 7d33ba57:1b82db35
2025-03-31 09:28:36Rovinj is one of Croatia’s most beautiful coastal towns, known for its colorful Venetian-style buildings, cobblestone streets, and breathtaking sea views. Located on the Istrian Peninsula, Rovinj offers a mix of history, culture, and stunning beaches, making it a perfect getaway for travelers seeking both relaxation and adventure.  ## **🌊 Top Things to See & Do in Rovinj** ### **1️⃣ Explore Rovinj Old Town 🏡** - Wander through **narrow, winding streets** filled with **art galleries, boutique shops, and charming cafés**. - Discover **Balbi’s Arch**, the old entrance to the city, and the **Clock Tower**. - Enjoy **stunning sunset views** from the harbor. ### **2️⃣ Visit St. Euphemia’s Church ⛪** - The **most famous landmark in Rovinj**, located at the highest point of the Old Town. - Climb the **bell tower** for a **panoramic view** of the Adriatic and nearby islands. - Learn about **Saint Euphemia**, the town’s patron saint, and her fascinating legend.  ### **3️⃣ Relax at Rovinj’s Best Beaches 🏖️** - **Lone Bay Beach** – A popular spot near Zlatni Rt forest, great for swimming. - **Mulini Beach** – A stylish beach with a cocktail bar and clear waters. - **Cuvi Beach** – A quieter, family-friendly pebble beach. ### **4️⃣ Walk or Cycle Through Golden Cape Forest Park (Zlatni Rt) 🌿🚲** - A **protected nature park** with pine forests, walking trails, and hidden coves. - Great for **hiking, cycling, and rock climbing**. - Perfect for a **picnic with sea views**. ### **5️⃣ Take a Boat Trip to Rovinj Archipelago 🛥️** - Explore **Red Island (Crveni Otok)** – A peaceful getaway with sandy beaches. - Visit **St. Andrew’s Island**, home to a former Benedictine monastery. - Sunset **dolphin-watching tours** are a must! 🐬  ### **6️⃣ Try Authentic Istrian Cuisine 🍽️** - **Fuži with truffles** – A local pasta dish with **Istria’s famous truffles**. - **Istrian seafood platter** – Fresh fish, mussels, and Adriatic shrimp. - **Olive oil & wine tasting** – Try local **Malvazija (white) and Teran (red) wines**. ### **7️⃣ Visit the Batana House Museum ⛵** - A **unique museum dedicated to Rovinj’s traditional wooden fishing boats (batanas)**. - Learn about **local fishing traditions and maritime culture**. - End the visit with a traditional **batana boat ride at sunset**.  ## **🚗 How to Get to Rovinj** ✈️ **By Air:** The nearest airport is **Pula Airport (PUY), 40 km away**. 🚘 **By Car:** - **From Pula:** ~40 min (40 km) - **From Zagreb:** ~3 hours (250 km) - **From Ljubljana (Slovenia):** ~2.5 hours (170 km) 🚌 **By Bus:** Direct buses from **Pula, Rijeka, and Zagreb**. 🚢 **By Ferry:** Seasonal ferries connect Rovinj with **Venice, Italy** (~2.5 hours).  ## **💡 Tips for Visiting Rovinj** ✅ **Best time to visit?** **May–September** for warm weather & festivals ☀️ ✅ **Wear comfy shoes** – The Old Town streets are made of polished stone & can be slippery 👟 ✅ **Book restaurants in advance** – Rovinj is a foodie hotspot, especially in summer 🍷 ✅ **Take a sunset walk along the harbor** – One of the most romantic views in Croatia 🌅 ✅ **Bring cash** – Some smaller shops and taverns still prefer cash 💶 
@ 7d33ba57:1b82db35
2025-03-31 09:28:36Rovinj is one of Croatia’s most beautiful coastal towns, known for its colorful Venetian-style buildings, cobblestone streets, and breathtaking sea views. Located on the Istrian Peninsula, Rovinj offers a mix of history, culture, and stunning beaches, making it a perfect getaway for travelers seeking both relaxation and adventure.  ## **🌊 Top Things to See & Do in Rovinj** ### **1️⃣ Explore Rovinj Old Town 🏡** - Wander through **narrow, winding streets** filled with **art galleries, boutique shops, and charming cafés**. - Discover **Balbi’s Arch**, the old entrance to the city, and the **Clock Tower**. - Enjoy **stunning sunset views** from the harbor. ### **2️⃣ Visit St. Euphemia’s Church ⛪** - The **most famous landmark in Rovinj**, located at the highest point of the Old Town. - Climb the **bell tower** for a **panoramic view** of the Adriatic and nearby islands. - Learn about **Saint Euphemia**, the town’s patron saint, and her fascinating legend.  ### **3️⃣ Relax at Rovinj’s Best Beaches 🏖️** - **Lone Bay Beach** – A popular spot near Zlatni Rt forest, great for swimming. - **Mulini Beach** – A stylish beach with a cocktail bar and clear waters. - **Cuvi Beach** – A quieter, family-friendly pebble beach. ### **4️⃣ Walk or Cycle Through Golden Cape Forest Park (Zlatni Rt) 🌿🚲** - A **protected nature park** with pine forests, walking trails, and hidden coves. - Great for **hiking, cycling, and rock climbing**. - Perfect for a **picnic with sea views**. ### **5️⃣ Take a Boat Trip to Rovinj Archipelago 🛥️** - Explore **Red Island (Crveni Otok)** – A peaceful getaway with sandy beaches. - Visit **St. Andrew’s Island**, home to a former Benedictine monastery. - Sunset **dolphin-watching tours** are a must! 🐬  ### **6️⃣ Try Authentic Istrian Cuisine 🍽️** - **Fuži with truffles** – A local pasta dish with **Istria’s famous truffles**. - **Istrian seafood platter** – Fresh fish, mussels, and Adriatic shrimp. - **Olive oil & wine tasting** – Try local **Malvazija (white) and Teran (red) wines**. ### **7️⃣ Visit the Batana House Museum ⛵** - A **unique museum dedicated to Rovinj’s traditional wooden fishing boats (batanas)**. - Learn about **local fishing traditions and maritime culture**. - End the visit with a traditional **batana boat ride at sunset**.  ## **🚗 How to Get to Rovinj** ✈️ **By Air:** The nearest airport is **Pula Airport (PUY), 40 km away**. 🚘 **By Car:** - **From Pula:** ~40 min (40 km) - **From Zagreb:** ~3 hours (250 km) - **From Ljubljana (Slovenia):** ~2.5 hours (170 km) 🚌 **By Bus:** Direct buses from **Pula, Rijeka, and Zagreb**. 🚢 **By Ferry:** Seasonal ferries connect Rovinj with **Venice, Italy** (~2.5 hours).  ## **💡 Tips for Visiting Rovinj** ✅ **Best time to visit?** **May–September** for warm weather & festivals ☀️ ✅ **Wear comfy shoes** – The Old Town streets are made of polished stone & can be slippery 👟 ✅ **Book restaurants in advance** – Rovinj is a foodie hotspot, especially in summer 🍷 ✅ **Take a sunset walk along the harbor** – One of the most romantic views in Croatia 🌅 ✅ **Bring cash** – Some smaller shops and taverns still prefer cash 💶  @ 78c90fc4:4bff983c
2025-03-31 08:13:17Die Operation „Cast Thy Bread“ war eine verdeckte Kampagne zur biologischen Kriegsführung, die von der Haganah und später von den israelischen Verteidigungsstreitkräften während des arabisch-israelischen Krieges 1948 durchgeführt wurde\[1]\[3]. Bei der Operation, die im April 1948 begann, wurden Trinkwasserquellen mit Typhusbakterien verseucht, um palästinensisch-arabische Zivilisten und verbündete arabische Armeen anzugreifen\[1]\[3]. 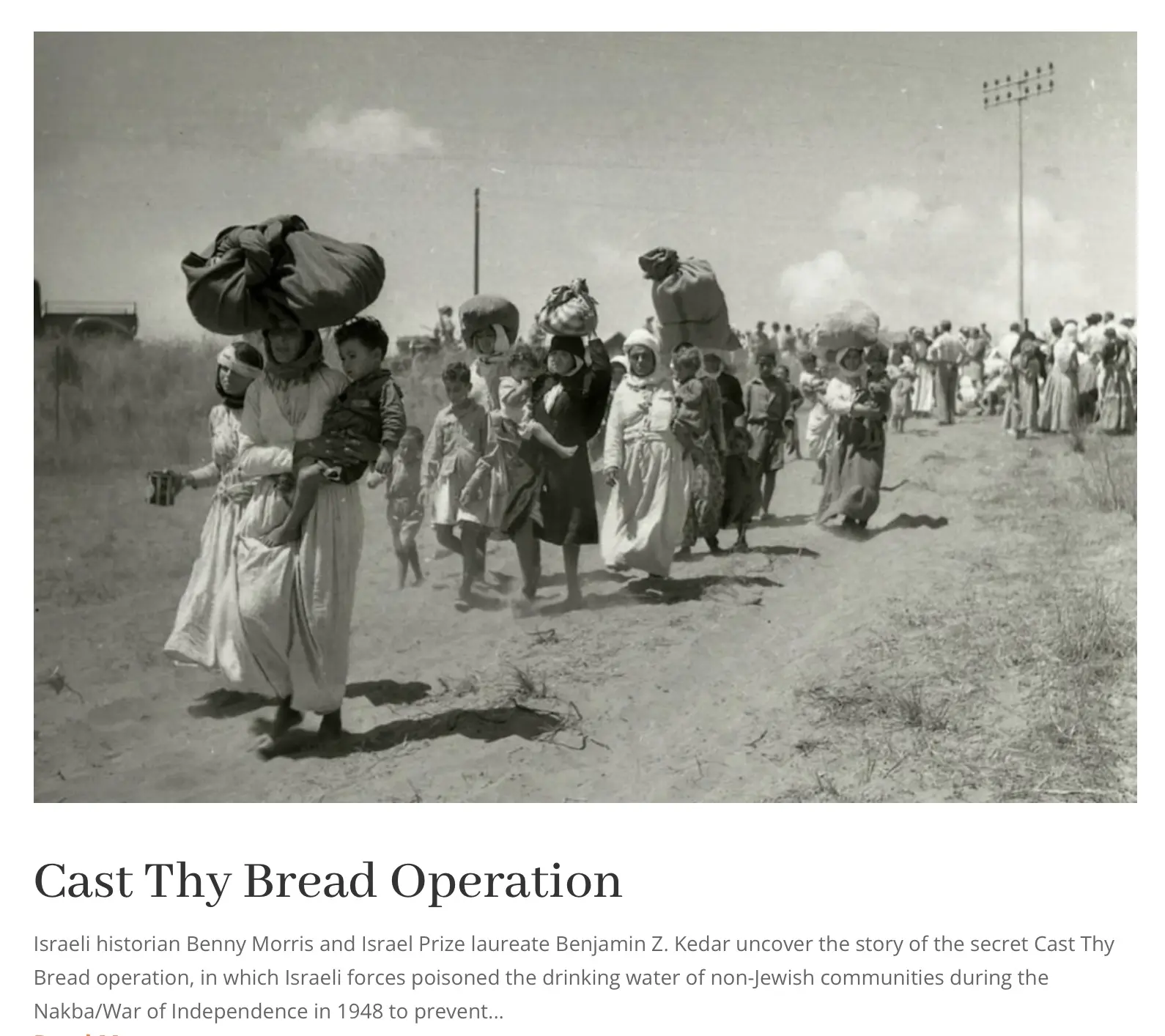 \ \ \## Wichtige Details\ \ \- \*\*Ziel\*\*: Palästinensische Araber an der Rückkehr in eroberte Dörfer zu hindern und die Versuche der arabischen Armeen, Gebiete zurückzuerobern, zu behindern\[1].\ \- \*\*Methoden\*\*: Israelische Streitkräfte setzten Typhuskeime in Flaschen, Reagenzgläsern und Thermoskannen ein, um Brunnen und Wasservorräte in palästinensischen Gebieten zu vergiften\[1]\[3].\ \- \*\*Führung\*\*: Die Operation wurde vom israelischen Premierminister David Ben-Gurion und dem Generalstabschef der IDF, Yigael Yadin, beaufsichtigt und genehmigt\[1].\ \ \## Bemerkenswerte Vorfälle\ \ \- Akkon (Akka)\*\*: Die Wasserversorgung der Stadt wurde am 15. Mai 1948 verseucht, was zu einer Typhusepidemie und „extremer Verzweiflung“ unter den Einwohnern führte\[1]\[3].\ \- \*\*Gaza\*\*: Im Mai 1948 versuchten vier Soldaten der israelischen Spezialeinheiten, die örtliche Wasserversorgung zu vergiften, wurden jedoch gefangen genommen und hingerichtet\[1].\ \- \*\*Andere Orte\*\*: Auch in Jericho, Eilabun und palästinensischen Vierteln in Jerusalem wurden Brunnen vergiftet\[1]\[3].\ \ \## Folgen\ \ Die Operation führte zu schweren Erkrankungen unter den palästinensischen Anwohnern, von denen Dutzende betroffen sein sollen\[1]\[3]. Sie erzielte jedoch nicht die von ihren Befürwortern erhoffte lähmende Wirkung und wurde im Dezember 1948 eingestellt\[1].\ \ \## Historische Bedeutung\ \ Die Operation „Gegossenes Brot“ wurde als Kriegsverbrechen und als Akt der ethnischen Säuberung eingestuft\[1]. Ihre Enthüllung hat eine Kontroverse und Debatte über die im Krieg von 1948 angewandten Taktiken und ihre langfristigen Auswirkungen auf den israelisch-palästinensischen Konflikt ausgelöst\[2]\[4]. Quellen \[1] Operation Cast Thy Bread - Wikipedia https\://en.wikipedia.org/wiki/Operation\_Cast\_Thy\_Bread \[2] Cast Thy Bread Archives - Promised Land Museum https\://promisedlandmuseum.org/tag/cast-thy-bread/ \[3] From 'Virtuous Boy' to Murderous Fanatic: David Ben-Gurion and the ... https\://www\.euppublishing.com/doi/10.3366/hlps.2023.0308 \[4] Historians reveal Israel's use of poison against Palestinians https\://www\.middleeastmonitor.com/20221011-historians-reveal-israels-use-of-poison-against-palestinians/ \[5] Thoughts on Operation Cast Thy Bread? : r/IsraelPalestine - Reddit https\://www\.reddit.com/r/IsraelPalestine/comments/1g02b64/thoughts\_on\_operation\_cast\_thy\_bread/ \[6] 'Cast thy bread': Israeli biological warfare during the 1948 War https\://www\.tandfonline.com/doi/abs/10.1080/00263206.2022.2122448 \[7] 'Cast thy bread': Israeli biological warfare during the 1948 War https\://cris.bgu.ac.il/en/publications/cast-thy-bread-israeli-biological-warfare-during-the-1948-war \[8] 'Cast thy bread': Israeli biological warfare during the 1948 War https\://www\.tandfonline.com/doi/full/10.1080/00263206.2022.2122448 \ Artikel <https://x.com/RealWsiegrist/status/1906616394747179136> Nakba <https://waltisiegrist.locals.com/upost/2033124/die-siedler-fordern-ganz-offen-eine-zweite-nakba>
@ 78c90fc4:4bff983c
2025-03-31 08:13:17Die Operation „Cast Thy Bread“ war eine verdeckte Kampagne zur biologischen Kriegsführung, die von der Haganah und später von den israelischen Verteidigungsstreitkräften während des arabisch-israelischen Krieges 1948 durchgeführt wurde\[1]\[3]. Bei der Operation, die im April 1948 begann, wurden Trinkwasserquellen mit Typhusbakterien verseucht, um palästinensisch-arabische Zivilisten und verbündete arabische Armeen anzugreifen\[1]\[3]. 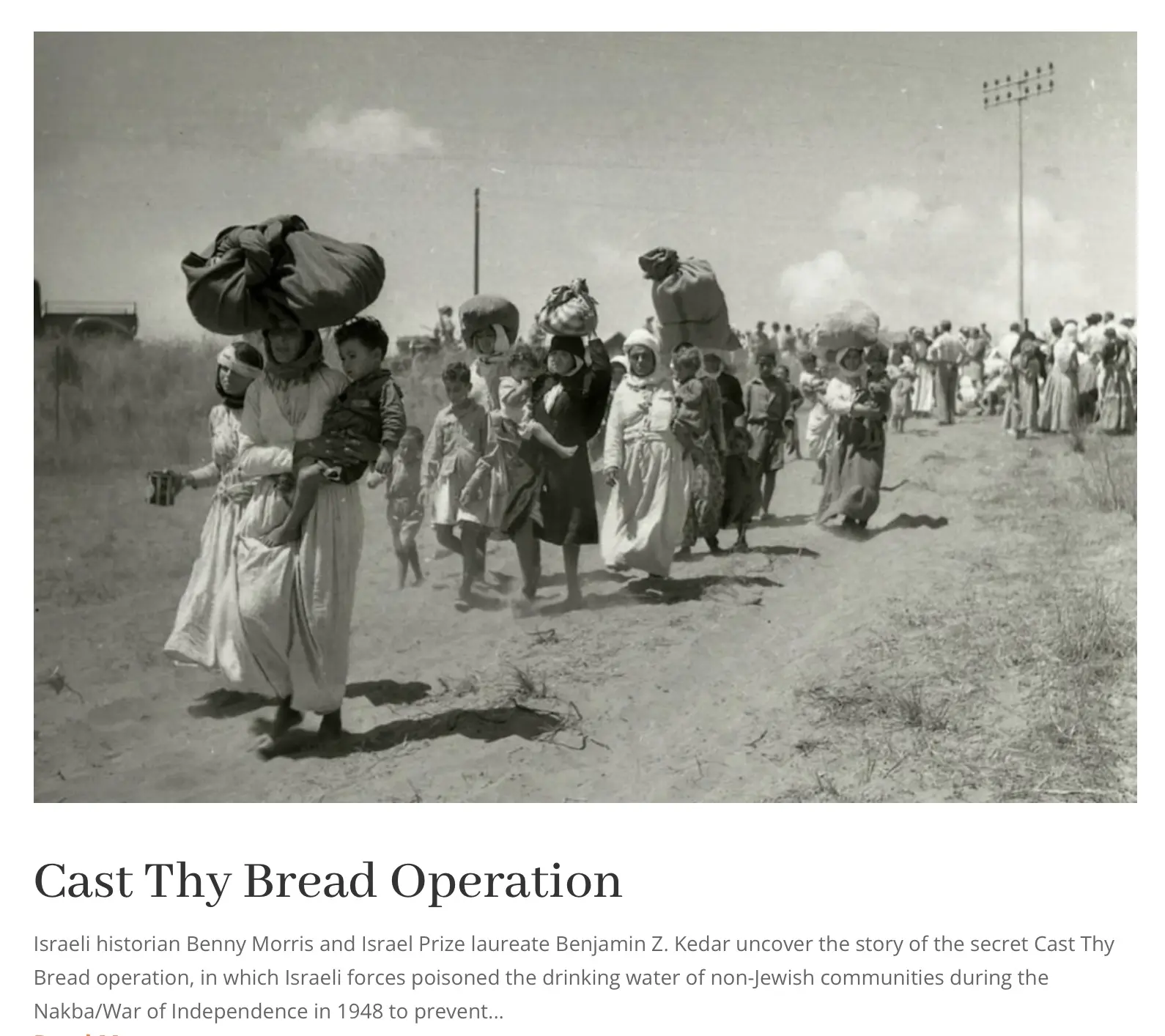 \ \ \## Wichtige Details\ \ \- \*\*Ziel\*\*: Palästinensische Araber an der Rückkehr in eroberte Dörfer zu hindern und die Versuche der arabischen Armeen, Gebiete zurückzuerobern, zu behindern\[1].\ \- \*\*Methoden\*\*: Israelische Streitkräfte setzten Typhuskeime in Flaschen, Reagenzgläsern und Thermoskannen ein, um Brunnen und Wasservorräte in palästinensischen Gebieten zu vergiften\[1]\[3].\ \- \*\*Führung\*\*: Die Operation wurde vom israelischen Premierminister David Ben-Gurion und dem Generalstabschef der IDF, Yigael Yadin, beaufsichtigt und genehmigt\[1].\ \ \## Bemerkenswerte Vorfälle\ \ \- Akkon (Akka)\*\*: Die Wasserversorgung der Stadt wurde am 15. Mai 1948 verseucht, was zu einer Typhusepidemie und „extremer Verzweiflung“ unter den Einwohnern führte\[1]\[3].\ \- \*\*Gaza\*\*: Im Mai 1948 versuchten vier Soldaten der israelischen Spezialeinheiten, die örtliche Wasserversorgung zu vergiften, wurden jedoch gefangen genommen und hingerichtet\[1].\ \- \*\*Andere Orte\*\*: Auch in Jericho, Eilabun und palästinensischen Vierteln in Jerusalem wurden Brunnen vergiftet\[1]\[3].\ \ \## Folgen\ \ Die Operation führte zu schweren Erkrankungen unter den palästinensischen Anwohnern, von denen Dutzende betroffen sein sollen\[1]\[3]. Sie erzielte jedoch nicht die von ihren Befürwortern erhoffte lähmende Wirkung und wurde im Dezember 1948 eingestellt\[1].\ \ \## Historische Bedeutung\ \ Die Operation „Gegossenes Brot“ wurde als Kriegsverbrechen und als Akt der ethnischen Säuberung eingestuft\[1]. Ihre Enthüllung hat eine Kontroverse und Debatte über die im Krieg von 1948 angewandten Taktiken und ihre langfristigen Auswirkungen auf den israelisch-palästinensischen Konflikt ausgelöst\[2]\[4]. Quellen \[1] Operation Cast Thy Bread - Wikipedia https\://en.wikipedia.org/wiki/Operation\_Cast\_Thy\_Bread \[2] Cast Thy Bread Archives - Promised Land Museum https\://promisedlandmuseum.org/tag/cast-thy-bread/ \[3] From 'Virtuous Boy' to Murderous Fanatic: David Ben-Gurion and the ... https\://www\.euppublishing.com/doi/10.3366/hlps.2023.0308 \[4] Historians reveal Israel's use of poison against Palestinians https\://www\.middleeastmonitor.com/20221011-historians-reveal-israels-use-of-poison-against-palestinians/ \[5] Thoughts on Operation Cast Thy Bread? : r/IsraelPalestine - Reddit https\://www\.reddit.com/r/IsraelPalestine/comments/1g02b64/thoughts\_on\_operation\_cast\_thy\_bread/ \[6] 'Cast thy bread': Israeli biological warfare during the 1948 War https\://www\.tandfonline.com/doi/abs/10.1080/00263206.2022.2122448 \[7] 'Cast thy bread': Israeli biological warfare during the 1948 War https\://cris.bgu.ac.il/en/publications/cast-thy-bread-israeli-biological-warfare-during-the-1948-war \[8] 'Cast thy bread': Israeli biological warfare during the 1948 War https\://www\.tandfonline.com/doi/full/10.1080/00263206.2022.2122448 \ Artikel <https://x.com/RealWsiegrist/status/1906616394747179136> Nakba <https://waltisiegrist.locals.com/upost/2033124/die-siedler-fordern-ganz-offen-eine-zweite-nakba> @ 0fa80bd3:ea7325de
2025-01-29 14:44:48![[yedinaya-rossiya-bear.png]] 1️⃣ Be where the bear roams. Stay in its territory, where it hunts for food. No point setting a trap in your backyard if the bear’s chilling in the forest. 2️⃣ Set a well-hidden trap. Bury it, disguise it, and place the bait right in the center. Bears are omnivores—just like secret police KGB agents. And what’s the tastiest bait for them? Money. 3️⃣ Wait for the bear to take the bait. When it reaches in, the trap will snap shut around its paw. It’ll be alive, but stuck. No escape. Now, what you do with a trapped bear is another question... 😏
@ 0fa80bd3:ea7325de
2025-01-29 14:44:48![[yedinaya-rossiya-bear.png]] 1️⃣ Be where the bear roams. Stay in its territory, where it hunts for food. No point setting a trap in your backyard if the bear’s chilling in the forest. 2️⃣ Set a well-hidden trap. Bury it, disguise it, and place the bait right in the center. Bears are omnivores—just like secret police KGB agents. And what’s the tastiest bait for them? Money. 3️⃣ Wait for the bear to take the bait. When it reaches in, the trap will snap shut around its paw. It’ll be alive, but stuck. No escape. Now, what you do with a trapped bear is another question... 😏 @ c631e267:c2b78d3e
2025-03-31 07:23:05*Der Irrsinn ist bei Einzelnen etwas Seltenes –* *\ aber bei Gruppen, Parteien, Völkern, Zeiten die Regel.* *\ Friedrich Nietzsche*   **Erinnern Sie sich an die Horrorkomödie «Scary Movie»?** Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?  **Diese Szene kommt mir automatisch in den Sinn,** wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real. **Die Europäische Union hat sich selbst über Jahre** konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt. **In den USA haben sich die Vorzeichen allerdings mittlerweile geändert,** und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen. **Statt jedoch umzukehren oder wenigstens zu bremsen** und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die [Kommentatoren](https://transition-news.org/wird-ihr-stahlhelm-schon-gegossen) des Events gegenseitig in sensationslüsterner «Berichterstattung». **Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen,** Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, [selbstzerstörerischen](https://transition-news.org/okonomen-eu-rustet-auf-und-schiesst-sich-selbst-ins-knie) Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», [erklärte](https://ec.europa.eu/commission/presscorner/detail/de/ip_25_793) die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte. **Zusätzlich brisant ist, dass aktuell «die ganze EU** **[von Deutschen regiert](https://transition-news.org/die-ganze-eu-wird-von-deutschen-regiert)** **wird»,** wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen. **Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung** hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen. **Es wird dringend Zeit, dass wir, der Souverän,** diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts [den Frieden auszurufen](https://transition-news.org/ein-zeichen-fur-die-friedliche-zukunft-europas-setzen). Seien wir dabei! *\[Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/vertical-abstract-concept-car-8992833/)]* *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/mit-vollgas-in-die-sackgasse)*** erschienen.
@ c631e267:c2b78d3e
2025-03-31 07:23:05*Der Irrsinn ist bei Einzelnen etwas Seltenes –* *\ aber bei Gruppen, Parteien, Völkern, Zeiten die Regel.* *\ Friedrich Nietzsche*   **Erinnern Sie sich an die Horrorkomödie «Scary Movie»?** Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?  **Diese Szene kommt mir automatisch in den Sinn,** wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real. **Die Europäische Union hat sich selbst über Jahre** konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt. **In den USA haben sich die Vorzeichen allerdings mittlerweile geändert,** und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen. **Statt jedoch umzukehren oder wenigstens zu bremsen** und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die [Kommentatoren](https://transition-news.org/wird-ihr-stahlhelm-schon-gegossen) des Events gegenseitig in sensationslüsterner «Berichterstattung». **Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen,** Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, [selbstzerstörerischen](https://transition-news.org/okonomen-eu-rustet-auf-und-schiesst-sich-selbst-ins-knie) Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», [erklärte](https://ec.europa.eu/commission/presscorner/detail/de/ip_25_793) die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte. **Zusätzlich brisant ist, dass aktuell «die ganze EU** **[von Deutschen regiert](https://transition-news.org/die-ganze-eu-wird-von-deutschen-regiert)** **wird»,** wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen. **Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung** hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen. **Es wird dringend Zeit, dass wir, der Souverän,** diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts [den Frieden auszurufen](https://transition-news.org/ein-zeichen-fur-die-friedliche-zukunft-europas-setzen). Seien wir dabei! *\[Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/vertical-abstract-concept-car-8992833/)]* *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/mit-vollgas-in-die-sackgasse)*** erschienen. @ 0fa80bd3:ea7325de
2025-01-29 05:55:02The land that belongs to the indigenous peoples of Russia has been seized by a gang of killers who have unleashed a war of extermination. They wipe out anyone who refuses to conform to their rules. Those who disagree and stay behind are tortured and killed in prisons and labor camps. Those who flee lose their homeland, dissolve into foreign cultures, and fade away. And those who stand up to protect their people are attacked by the misled and deceived. The deceived die for the unchecked greed of a single dictator—thousands from both sides, people who just wanted to live, raise their kids, and build a future. Now, they are forced to make an impossible choice: abandon their homeland or die. Some perish on the battlefield, others lose themselves in exile, stripped of their identity, scattered in a world that isn’t theirs. There’s been endless debate about how to fix this, how to clear the field of the weeds that choke out every new sprout, every attempt at change. But the real problem? We can’t play by their rules. We can’t speak their language or use their weapons. We stand for humanity, and no matter how righteous our cause, we will not multiply suffering. Victory doesn’t come from matching the enemy—it comes from staying ahead, from using tools they haven’t mastered yet. That’s how wars are won. Our only resource is the **will of the people** to rewrite the order of things. Historian Timothy Snyder once said that a nation cannot exist without a city. A city is where the most active part of a nation thrives. But the cities are occupied. The streets are watched. Gatherings are impossible. They control the money. They control the mail. They control the media. And any dissent is crushed before it can take root. So I started asking myself: **How do we stop this fragmentation?** How do we create a space where people can **rebuild their connections** when they’re ready? How do we build a **self-sustaining network**, where everyone contributes and benefits proportionally, while keeping their freedom to leave intact? And more importantly—**how do we make it spread, even in occupied territory?** In 2009, something historic happened: **the internet got its own money.** Thanks to **Satoshi Nakamoto**, the world took a massive leap forward. Bitcoin and decentralized ledgers shattered the idea that money must be controlled by the state. Now, to move or store value, all you need is an address and a key. A tiny string of text, easy to carry, impossible to seize. That was the year money broke free. The state lost its grip. Its biggest weapon—physical currency—became irrelevant. Money became **purely digital.** The internet was already **a sanctuary for information**, a place where people could connect and organize. But with Bitcoin, it evolved. Now, **value itself** could flow freely, beyond the reach of authorities. Think about it: when seedlings are grown in controlled environments before being planted outside, they **get stronger, survive longer, and bear fruit faster.** That’s how we handle crops in harsh climates—nurture them until they’re ready for the wild. Now, picture the internet as that **controlled environment** for **ideas**. Bitcoin? It’s the **fertile soil** that lets them grow. A testing ground for new models of interaction, where concepts can take root before they move into the real world. If **nation-states are a battlefield, locked in a brutal war for territory, the internet is boundless.** It can absorb any number of ideas, any number of people, and it doesn’t **run out of space.** But for this ecosystem to thrive, people need safe ways to communicate, to share ideas, to build something real—**without surveillance, without censorship, without the constant fear of being erased.** This is where **Nostr** comes in. Nostr—"Notes and Other Stuff Transmitted by Relays"—is more than just a messaging protocol. **It’s a new kind of city.** One that **no dictator can seize**, no corporation can own, no government can shut down. It’s built on **decentralization, encryption, and individual control.** Messages don’t pass through central servers—they are relayed through independent nodes, and users choose which ones to trust. There’s no master switch to shut it all down. Every person owns their identity, their data, their connections. And no one—no state, no tech giant, no algorithm—can silence them. In a world where cities fall and governments fail, **Nostr is a city that cannot be occupied.** A place for ideas, for networks, for freedom. A city that grows stronger **the more people build within it**.
@ 0fa80bd3:ea7325de
2025-01-29 05:55:02The land that belongs to the indigenous peoples of Russia has been seized by a gang of killers who have unleashed a war of extermination. They wipe out anyone who refuses to conform to their rules. Those who disagree and stay behind are tortured and killed in prisons and labor camps. Those who flee lose their homeland, dissolve into foreign cultures, and fade away. And those who stand up to protect their people are attacked by the misled and deceived. The deceived die for the unchecked greed of a single dictator—thousands from both sides, people who just wanted to live, raise their kids, and build a future. Now, they are forced to make an impossible choice: abandon their homeland or die. Some perish on the battlefield, others lose themselves in exile, stripped of their identity, scattered in a world that isn’t theirs. There’s been endless debate about how to fix this, how to clear the field of the weeds that choke out every new sprout, every attempt at change. But the real problem? We can’t play by their rules. We can’t speak their language or use their weapons. We stand for humanity, and no matter how righteous our cause, we will not multiply suffering. Victory doesn’t come from matching the enemy—it comes from staying ahead, from using tools they haven’t mastered yet. That’s how wars are won. Our only resource is the **will of the people** to rewrite the order of things. Historian Timothy Snyder once said that a nation cannot exist without a city. A city is where the most active part of a nation thrives. But the cities are occupied. The streets are watched. Gatherings are impossible. They control the money. They control the mail. They control the media. And any dissent is crushed before it can take root. So I started asking myself: **How do we stop this fragmentation?** How do we create a space where people can **rebuild their connections** when they’re ready? How do we build a **self-sustaining network**, where everyone contributes and benefits proportionally, while keeping their freedom to leave intact? And more importantly—**how do we make it spread, even in occupied territory?** In 2009, something historic happened: **the internet got its own money.** Thanks to **Satoshi Nakamoto**, the world took a massive leap forward. Bitcoin and decentralized ledgers shattered the idea that money must be controlled by the state. Now, to move or store value, all you need is an address and a key. A tiny string of text, easy to carry, impossible to seize. That was the year money broke free. The state lost its grip. Its biggest weapon—physical currency—became irrelevant. Money became **purely digital.** The internet was already **a sanctuary for information**, a place where people could connect and organize. But with Bitcoin, it evolved. Now, **value itself** could flow freely, beyond the reach of authorities. Think about it: when seedlings are grown in controlled environments before being planted outside, they **get stronger, survive longer, and bear fruit faster.** That’s how we handle crops in harsh climates—nurture them until they’re ready for the wild. Now, picture the internet as that **controlled environment** for **ideas**. Bitcoin? It’s the **fertile soil** that lets them grow. A testing ground for new models of interaction, where concepts can take root before they move into the real world. If **nation-states are a battlefield, locked in a brutal war for territory, the internet is boundless.** It can absorb any number of ideas, any number of people, and it doesn’t **run out of space.** But for this ecosystem to thrive, people need safe ways to communicate, to share ideas, to build something real—**without surveillance, without censorship, without the constant fear of being erased.** This is where **Nostr** comes in. Nostr—"Notes and Other Stuff Transmitted by Relays"—is more than just a messaging protocol. **It’s a new kind of city.** One that **no dictator can seize**, no corporation can own, no government can shut down. It’s built on **decentralization, encryption, and individual control.** Messages don’t pass through central servers—they are relayed through independent nodes, and users choose which ones to trust. There’s no master switch to shut it all down. Every person owns their identity, their data, their connections. And no one—no state, no tech giant, no algorithm—can silence them. In a world where cities fall and governments fail, **Nostr is a city that cannot be occupied.** A place for ideas, for networks, for freedom. A city that grows stronger **the more people build within it**. @ 9e69e420:d12360c2
2025-01-26 15:26:44Secretary of State Marco Rubio issued new guidance halting spending on most foreign aid grants for 90 days, including military assistance to Ukraine. This immediate order shocked State Department officials and mandates “stop-work orders” on nearly all existing foreign assistance awards. While it allows exceptions for military financing to Egypt and Israel, as well as emergency food assistance, it restricts aid to key allies like Ukraine, Jordan, and Taiwan. The guidance raises potential liability risks for the government due to unfulfilled contracts. A report will be prepared within 85 days to recommend which programs to continue or discontinue.
@ 9e69e420:d12360c2
2025-01-26 15:26:44Secretary of State Marco Rubio issued new guidance halting spending on most foreign aid grants for 90 days, including military assistance to Ukraine. This immediate order shocked State Department officials and mandates “stop-work orders” on nearly all existing foreign assistance awards. While it allows exceptions for military financing to Egypt and Israel, as well as emergency food assistance, it restricts aid to key allies like Ukraine, Jordan, and Taiwan. The guidance raises potential liability risks for the government due to unfulfilled contracts. A report will be prepared within 85 days to recommend which programs to continue or discontinue. @ 78c90fc4:4bff983c
2025-03-31 07:03:41In Palästina und im Ausland wurde das Abkommen einzelner jüdischer Organisationen mit dem [nationalsozialistischen Deutschland](https://de.m.wikipedia.org/wiki/Deutsches_Reich_1933_bis_1945) heftig kritisiert. Auf dem 18. [Zionistenkongress](https://de.m.wikipedia.org/wiki/Zionistenkongress) 1933 in Prag etwa bezeichnete der Schriftsteller [Schalom Asch](https://de.m.wikipedia.org/wiki/Schalom_Asch) das Abkommen mit [Hitlers Regime](https://de.m.wikipedia.org/wiki/NS-Regime) als „Verrat am Weltjudentum“. [Chaim Arlosoroff](https://de.m.wikipedia.org/wiki/Chaim_Arlosoroff), der damalige Verhandlungsführer der Jewish Agency, wurde wahrscheinlich deshalb im Juni 1933 Opfer [eines Mordanschlags](https://de.m.wikipedia.org/wiki/Chaim_Arlosoroff#Ermordung).    https\://de.m.wikipedia.org/wiki/Ha’avara-Abkommen Am 16. Juni 1933 wurde Chaim Arlosoroff kurz nach seiner Rückkehr von den Transfer-Verhandlungen in Deutschland durch den Pistolenschuss eines Attentäters schwer verletzt, als er mit seiner Frau Sima, geb. Rubin, am Strand von Tel Aviv entlangging. Er verstarb am folgenden Tag im Krankenhaus. Wer der Attentäter war, ist bis heute ungeklärt. Zunächst wurden drei Verdächtige angeklagt. Zwei von ihnen wurden freigesprochen, einer, [Abraham Stavsky](https://de.m.wikipedia.org/wiki/Abraham_Stavsky), wurde verurteilt, doch das Urteil wurde durch das oberste Appellationsgericht aufgehoben. <https://de.m.wikipedia.org/wiki/Chaim_Arlosoroff#Ermordung> **Instrumentalisierung des Holocaust** Von Anneliese Fikentscher und Andreas Neumann Zum Schluss ein Zitat aus dem 2017 erschienenen Buch "Die israelisch-jüdische Tragödie. Von Auschwitz zum Besatzungs- und Apartheidstaat. Das Ende der Verklärung" von Arn Strohmeyer: „Der vielleicht radikalste Kritiker des israelischen Holocaustgedenkens ist der amerikanisch -jüdische Politologe Norman Finkelstein. Er wendet sich vor allem gegen das in Israel und den USA verwendete Dogma, der Holocaust sei 'einzigartig' gewesen und mit anderen Verbrechen nicht vergleichbar, dass er in der Geschichte also ohne Parallele sei. Diese Behauptung – so Finkelstein – impliziert eine Reihe anderer Behauptungen, die wiederum die Instrumentalisierung des Holocaust ausmachen. Erstens: Die Konstruktion des Holocaust als einzigartig gilt als gegeben, sie zu leugnen gilt als Leugnung des Holocaust. Diese Behauptung schließt zweitens ein rationales Verständnis des Holocaust aus, er macht den Holocaust zu einem Mysterium, wie Elie Wiesel ihn verstanden hat. Einzigartiges Leid verleiht drittens einen einzigartigen Anspruch. Die Unvergleichlichkeit des Holocaust stellt also ein moralisches Kapital dar, das Israel als politisches Alibi benutzt. Israel kann – so Finkelstein – diese moralischen und emotionalen Ansprüche an andere Staaten stellen und die Anerkennung seines Rechts einfordern, dass es als besonders bedroht gelten kann und seine Anstrengungen zum Überleben der Unterstützung bedarf. Die Behauptung der Einzigartigkeit des Holocaust beinhaltet auch die Behauptung der jüdischen Einzigartigkeit. Der Holocaust ist also etwas Besonderes, weil Juden etwas Besonderes sind, was man als säkularisierte Version der Auserwähltheit deuten kann. Diese Behauptungen – so Finkelstein – sollen Israels Sonderstellung legitimieren, sollen von vornherein jede unmenschliche Behandlung von Nichtjuden entschuldigen (Israel ist 'alles erlaubt!') und machen diesen Staat und seine Politik gegen jede Kritik immun. Bei dieser Instrumentalisierung des Holocaust bleiben die Rechte und die Würde der Opfer – welcher auch immer – völlig auf der Strecke.“ Ist das einer breiten Öffentlichkeit bewusst? <http://www.nrhz.de/flyer/beitrag.php?id=24469> Perplexity: Der Schriftsteller Schalom Asch kritisierte das Ha'avara-Abkommen scharf auf dem 18. Zionistischen Kongress, der vom 21. August bis 4. September 1933 in Prag stattfand. Er bezeichnete das Abkommen mit dem Hitler-Regime als "ein Verrat am Weltjudentum"\[1]\[2]. Das Ha'avara-Abkommen wurde am 10. August 1933 zwischen der Jewish Agency, der Zionistischen Vereinigung für Deutschland und dem deutschen Reichsministerium für Wirtschaft geschlossen. Es sollte die Emigration deutscher Juden nach Palästina erleichtern und gleichzeitig den deutschen Export fördern\[2]. Am 5. November 1933 wurde die "Trust and Transfer Office Ha'avara Ltd." als quasi privates Unternehmen eingetragen\[1]\[3]. Trotz der anfänglichen Kritik billigte die Zionistische Weltorganisation auf ihrer Konferenz am 20. August 1935 in Luzern mit Mehrheit den Ha'avara-Abschluss und übernahm sogar dessen gesamte Tätigkeit in eigene Regie\[1]\[2]\[3]. Das Abkommen war innerhalb der zionistischen Bewegung umstritten, da es den gleichzeitig vorangetriebenen Boykottmaßnahmen gegen die Nationalsozialisten zuwiderlief\[2]. Es ermöglichte deutschen Juden, einen Teil ihres Vermögens nach Palästina zu transferieren, wobei ein bestimmter Prozentsatz als Reichsfluchtsteuer vom deutschen Fiskus einbehalten wurde\[5]. Quellen \[1] Zionistenkongress - Wikiwand https\://www\.wikiwand.com/de/articles/Zionistenkongress \[2] Ha'avara-Abkommen - Wikiwand https\://www\.wikiwand.com/de/articles/Haavara-Abkommen \[3] Zionistenkongress - Wikipedia https\://de.wikipedia.org/wiki/Zionistenkongress \[4] Schalom Asch - Wikipedia https\://de.wikipedia.org/wiki/Schalom\_Asch \[5] Ha'avara-Abkommen - Wikipedia https\://de.wikipedia.org/wiki/Ha%E2%80%99avara-Abkommen \[6] Stefan Zweig. Briefe zum Judentum. Hg. v. Stefan Litt. Berlin ... https\://judaica.ch/article/view/8320/11519 \[7] Das Haavara-Transfer-Abkommen | Die Wohnung | bpb.de https\://www\.bpb.de/themen/nationalsozialismus-zweiter-weltkrieg/die-wohnung/195259/das-haavara-transfer-abkommen/ \[8] Jüdischer Verlag - Wikipedia https\://de.wikipedia.org/wiki/J%C3%BCdischer\_Verlag Artikel <https://x.com/RealWsiegrist/status/1906601705355252211>
@ 78c90fc4:4bff983c
2025-03-31 07:03:41In Palästina und im Ausland wurde das Abkommen einzelner jüdischer Organisationen mit dem [nationalsozialistischen Deutschland](https://de.m.wikipedia.org/wiki/Deutsches_Reich_1933_bis_1945) heftig kritisiert. Auf dem 18. [Zionistenkongress](https://de.m.wikipedia.org/wiki/Zionistenkongress) 1933 in Prag etwa bezeichnete der Schriftsteller [Schalom Asch](https://de.m.wikipedia.org/wiki/Schalom_Asch) das Abkommen mit [Hitlers Regime](https://de.m.wikipedia.org/wiki/NS-Regime) als „Verrat am Weltjudentum“. [Chaim Arlosoroff](https://de.m.wikipedia.org/wiki/Chaim_Arlosoroff), der damalige Verhandlungsführer der Jewish Agency, wurde wahrscheinlich deshalb im Juni 1933 Opfer [eines Mordanschlags](https://de.m.wikipedia.org/wiki/Chaim_Arlosoroff#Ermordung).    https\://de.m.wikipedia.org/wiki/Ha’avara-Abkommen Am 16. Juni 1933 wurde Chaim Arlosoroff kurz nach seiner Rückkehr von den Transfer-Verhandlungen in Deutschland durch den Pistolenschuss eines Attentäters schwer verletzt, als er mit seiner Frau Sima, geb. Rubin, am Strand von Tel Aviv entlangging. Er verstarb am folgenden Tag im Krankenhaus. Wer der Attentäter war, ist bis heute ungeklärt. Zunächst wurden drei Verdächtige angeklagt. Zwei von ihnen wurden freigesprochen, einer, [Abraham Stavsky](https://de.m.wikipedia.org/wiki/Abraham_Stavsky), wurde verurteilt, doch das Urteil wurde durch das oberste Appellationsgericht aufgehoben. <https://de.m.wikipedia.org/wiki/Chaim_Arlosoroff#Ermordung> **Instrumentalisierung des Holocaust** Von Anneliese Fikentscher und Andreas Neumann Zum Schluss ein Zitat aus dem 2017 erschienenen Buch "Die israelisch-jüdische Tragödie. Von Auschwitz zum Besatzungs- und Apartheidstaat. Das Ende der Verklärung" von Arn Strohmeyer: „Der vielleicht radikalste Kritiker des israelischen Holocaustgedenkens ist der amerikanisch -jüdische Politologe Norman Finkelstein. Er wendet sich vor allem gegen das in Israel und den USA verwendete Dogma, der Holocaust sei 'einzigartig' gewesen und mit anderen Verbrechen nicht vergleichbar, dass er in der Geschichte also ohne Parallele sei. Diese Behauptung – so Finkelstein – impliziert eine Reihe anderer Behauptungen, die wiederum die Instrumentalisierung des Holocaust ausmachen. Erstens: Die Konstruktion des Holocaust als einzigartig gilt als gegeben, sie zu leugnen gilt als Leugnung des Holocaust. Diese Behauptung schließt zweitens ein rationales Verständnis des Holocaust aus, er macht den Holocaust zu einem Mysterium, wie Elie Wiesel ihn verstanden hat. Einzigartiges Leid verleiht drittens einen einzigartigen Anspruch. Die Unvergleichlichkeit des Holocaust stellt also ein moralisches Kapital dar, das Israel als politisches Alibi benutzt. Israel kann – so Finkelstein – diese moralischen und emotionalen Ansprüche an andere Staaten stellen und die Anerkennung seines Rechts einfordern, dass es als besonders bedroht gelten kann und seine Anstrengungen zum Überleben der Unterstützung bedarf. Die Behauptung der Einzigartigkeit des Holocaust beinhaltet auch die Behauptung der jüdischen Einzigartigkeit. Der Holocaust ist also etwas Besonderes, weil Juden etwas Besonderes sind, was man als säkularisierte Version der Auserwähltheit deuten kann. Diese Behauptungen – so Finkelstein – sollen Israels Sonderstellung legitimieren, sollen von vornherein jede unmenschliche Behandlung von Nichtjuden entschuldigen (Israel ist 'alles erlaubt!') und machen diesen Staat und seine Politik gegen jede Kritik immun. Bei dieser Instrumentalisierung des Holocaust bleiben die Rechte und die Würde der Opfer – welcher auch immer – völlig auf der Strecke.“ Ist das einer breiten Öffentlichkeit bewusst? <http://www.nrhz.de/flyer/beitrag.php?id=24469> Perplexity: Der Schriftsteller Schalom Asch kritisierte das Ha'avara-Abkommen scharf auf dem 18. Zionistischen Kongress, der vom 21. August bis 4. September 1933 in Prag stattfand. Er bezeichnete das Abkommen mit dem Hitler-Regime als "ein Verrat am Weltjudentum"\[1]\[2]. Das Ha'avara-Abkommen wurde am 10. August 1933 zwischen der Jewish Agency, der Zionistischen Vereinigung für Deutschland und dem deutschen Reichsministerium für Wirtschaft geschlossen. Es sollte die Emigration deutscher Juden nach Palästina erleichtern und gleichzeitig den deutschen Export fördern\[2]. Am 5. November 1933 wurde die "Trust and Transfer Office Ha'avara Ltd." als quasi privates Unternehmen eingetragen\[1]\[3]. Trotz der anfänglichen Kritik billigte die Zionistische Weltorganisation auf ihrer Konferenz am 20. August 1935 in Luzern mit Mehrheit den Ha'avara-Abschluss und übernahm sogar dessen gesamte Tätigkeit in eigene Regie\[1]\[2]\[3]. Das Abkommen war innerhalb der zionistischen Bewegung umstritten, da es den gleichzeitig vorangetriebenen Boykottmaßnahmen gegen die Nationalsozialisten zuwiderlief\[2]. Es ermöglichte deutschen Juden, einen Teil ihres Vermögens nach Palästina zu transferieren, wobei ein bestimmter Prozentsatz als Reichsfluchtsteuer vom deutschen Fiskus einbehalten wurde\[5]. Quellen \[1] Zionistenkongress - Wikiwand https\://www\.wikiwand.com/de/articles/Zionistenkongress \[2] Ha'avara-Abkommen - Wikiwand https\://www\.wikiwand.com/de/articles/Haavara-Abkommen \[3] Zionistenkongress - Wikipedia https\://de.wikipedia.org/wiki/Zionistenkongress \[4] Schalom Asch - Wikipedia https\://de.wikipedia.org/wiki/Schalom\_Asch \[5] Ha'avara-Abkommen - Wikipedia https\://de.wikipedia.org/wiki/Ha%E2%80%99avara-Abkommen \[6] Stefan Zweig. Briefe zum Judentum. Hg. v. Stefan Litt. Berlin ... https\://judaica.ch/article/view/8320/11519 \[7] Das Haavara-Transfer-Abkommen | Die Wohnung | bpb.de https\://www\.bpb.de/themen/nationalsozialismus-zweiter-weltkrieg/die-wohnung/195259/das-haavara-transfer-abkommen/ \[8] Jüdischer Verlag - Wikipedia https\://de.wikipedia.org/wiki/J%C3%BCdischer\_Verlag Artikel <https://x.com/RealWsiegrist/status/1906601705355252211> @ da0b9bc3:4e30a4a9
2025-03-31 06:32:43Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/929968
@ da0b9bc3:4e30a4a9
2025-03-31 06:32:43Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/929968 @ 9e69e420:d12360c2
2025-01-26 01:31:31## Chef's notes # arbitray - test - of - chefs notes ## hedding 2 ## Details - ⏲️ Prep time: 20 - 🍳 Cook time: 1 hour - 🍽️ Servings: 5 ## Ingredients - Test ingredient - 2nd test ingredient ## Directions 1. Bake 2. Cool
@ 9e69e420:d12360c2
2025-01-26 01:31:31## Chef's notes # arbitray - test - of - chefs notes ## hedding 2 ## Details - ⏲️ Prep time: 20 - 🍳 Cook time: 1 hour - 🍽️ Servings: 5 ## Ingredients - Test ingredient - 2nd test ingredient ## Directions 1. Bake 2. Cool @ 9e69e420:d12360c2
2025-01-25 22:16:54President Trump plans to withdraw 20,000 U.S. troops from Europe and expects European allies to contribute financially to the remaining military presence. Reported by ANSA, Trump aims to deliver this message to European leaders since taking office. A European diplomat noted, “the costs cannot be borne solely by American taxpayers.” The Pentagon hasn't commented yet. Trump has previously sought lower troop levels in Europe and had ordered cuts during his first term. The U.S. currently maintains around 65,000 troops in Europe, with total forces reaching 100,000 since the Ukraine invasion. Trump's new approach may shift military focus to the Pacific amid growing concerns about China. [Sauce](https://www.stripes.com/theaters/europe/2025-01-24/trump-europe-troop-cuts-16590074.html)
@ 9e69e420:d12360c2
2025-01-25 22:16:54President Trump plans to withdraw 20,000 U.S. troops from Europe and expects European allies to contribute financially to the remaining military presence. Reported by ANSA, Trump aims to deliver this message to European leaders since taking office. A European diplomat noted, “the costs cannot be borne solely by American taxpayers.” The Pentagon hasn't commented yet. Trump has previously sought lower troop levels in Europe and had ordered cuts during his first term. The U.S. currently maintains around 65,000 troops in Europe, with total forces reaching 100,000 since the Ukraine invasion. Trump's new approach may shift military focus to the Pacific amid growing concerns about China. [Sauce](https://www.stripes.com/theaters/europe/2025-01-24/trump-europe-troop-cuts-16590074.html) @ 6be5cc06:5259daf0
2025-01-21 20:58:37A seguir, veja como instalar e configurar o **Privoxy** no **Pop!_OS**. --- ### **1. Instalar o Tor e o Privoxy** Abra o terminal e execute: ```bash sudo apt update sudo apt install tor privoxy ``` **Explicação:** - **Tor:** Roteia o tráfego pela rede Tor. - **Privoxy:** Proxy avançado que intermedia a conexão entre aplicativos e o Tor. --- ### **2. Configurar o Privoxy** Abra o arquivo de configuração do Privoxy: ```bash sudo nano /etc/privoxy/config ``` Navegue até a última linha (atalho: **`Ctrl`** + **`/`** depois **`Ctrl`** + **`V`** para navegar diretamente até a última linha) e insira: ```bash forward-socks5 / 127.0.0.1:9050 . ``` Isso faz com que o **Privoxy** envie todo o tráfego para o **Tor** através da porta **9050**. Salve (**`CTRL`** + **`O`** e **`Enter`**) e feche (**`CTRL`** + **`X`**) o arquivo. --- ### **3. Iniciar o Tor e o Privoxy** Agora, inicie e habilite os serviços: ```bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxy ``` **Explicação:** - **start:** Inicia os serviços. - **enable:** Faz com que iniciem automaticamente ao ligar o PC. --- ### **4. Configurar o Navegador Firefox** Para usar a rede **Tor** com o Firefox: 1. Abra o Firefox. 2. Acesse **Configurações** → **Configurar conexão**. 3. Selecione **Configuração manual de proxy**. 4. Configure assim: - **Proxy HTTP:** `127.0.0.1` - **Porta:** `8118` (porta padrão do **Privoxy**) - **Domínio SOCKS (v5):** `127.0.0.1` - **Porta:** `9050` 5. Marque a opção **"Usar este proxy também em HTTPS"**. 6. Clique em **OK**. --- ### **5. Verificar a Conexão com o Tor** Abra o navegador e acesse: ```text https://check.torproject.org/ ``` Se aparecer a mensagem **"Congratulations. This browser is configured to use Tor."**, a configuração está correta. --- ### **Dicas Extras** - **Privoxy** pode ser ajustado para bloquear anúncios e rastreadores. - Outros aplicativos também podem ser configurados para usar o **Privoxy**.
@ 6be5cc06:5259daf0
2025-01-21 20:58:37A seguir, veja como instalar e configurar o **Privoxy** no **Pop!_OS**. --- ### **1. Instalar o Tor e o Privoxy** Abra o terminal e execute: ```bash sudo apt update sudo apt install tor privoxy ``` **Explicação:** - **Tor:** Roteia o tráfego pela rede Tor. - **Privoxy:** Proxy avançado que intermedia a conexão entre aplicativos e o Tor. --- ### **2. Configurar o Privoxy** Abra o arquivo de configuração do Privoxy: ```bash sudo nano /etc/privoxy/config ``` Navegue até a última linha (atalho: **`Ctrl`** + **`/`** depois **`Ctrl`** + **`V`** para navegar diretamente até a última linha) e insira: ```bash forward-socks5 / 127.0.0.1:9050 . ``` Isso faz com que o **Privoxy** envie todo o tráfego para o **Tor** através da porta **9050**. Salve (**`CTRL`** + **`O`** e **`Enter`**) e feche (**`CTRL`** + **`X`**) o arquivo. --- ### **3. Iniciar o Tor e o Privoxy** Agora, inicie e habilite os serviços: ```bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxy ``` **Explicação:** - **start:** Inicia os serviços. - **enable:** Faz com que iniciem automaticamente ao ligar o PC. --- ### **4. Configurar o Navegador Firefox** Para usar a rede **Tor** com o Firefox: 1. Abra o Firefox. 2. Acesse **Configurações** → **Configurar conexão**. 3. Selecione **Configuração manual de proxy**. 4. Configure assim: - **Proxy HTTP:** `127.0.0.1` - **Porta:** `8118` (porta padrão do **Privoxy**) - **Domínio SOCKS (v5):** `127.0.0.1` - **Porta:** `9050` 5. Marque a opção **"Usar este proxy também em HTTPS"**. 6. Clique em **OK**. --- ### **5. Verificar a Conexão com o Tor** Abra o navegador e acesse: ```text https://check.torproject.org/ ``` Se aparecer a mensagem **"Congratulations. This browser is configured to use Tor."**, a configuração está correta. --- ### **Dicas Extras** - **Privoxy** pode ser ajustado para bloquear anúncios e rastreadores. - Outros aplicativos também podem ser configurados para usar o **Privoxy**. @ 9e69e420:d12360c2
2025-01-21 19:31:48Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits. ## Active Compounds The oil's therapeutic properties stem from its key bioactive components: - Carvacrol and thymol (primary active compounds) - Polyphenols and other antioxidant ## Antimicrobial Properties **Bacterial Protection** The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance. **Antifungal Effects** It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections. ## Digestive Health Benefits Oregano oil supports digestive wellness by: - Promoting gastric juice secretion and enzyme production - Helping treat Small Intestinal Bacterial Overgrowth (SIBO) - Managing digestive discomfort, bloating, and IBS symptoms ## Anti-inflammatory and Antioxidant Effects The oil provides significant protective benefits through: - Powerful antioxidant activity that fights free radicals - Reduction of inflammatory markers in the body - Protection against oxidative stress-related conditions ## Respiratory Support It aids respiratory health by: - Loosening mucus and phlegm - Suppressing coughs and throat irritation - Supporting overall respiratory tract function ## Additional Benefits **Skin Health** - Improves conditions like psoriasis, acne, and eczema - Supports wound healing through antibacterial action - Provides anti-aging benefits through antioxidant properties **Cardiovascular Health** Studies show oregano oil may help: - Reduce LDL (bad) cholesterol levels - Support overall heart health **Pain Management** The oil demonstrates effectiveness in: - Reducing inflammation-related pain - Managing muscle discomfort - Providing topical pain relief ## Safety Note While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications.
@ 9e69e420:d12360c2
2025-01-21 19:31:48Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits. ## Active Compounds The oil's therapeutic properties stem from its key bioactive components: - Carvacrol and thymol (primary active compounds) - Polyphenols and other antioxidant ## Antimicrobial Properties **Bacterial Protection** The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance. **Antifungal Effects** It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections. ## Digestive Health Benefits Oregano oil supports digestive wellness by: - Promoting gastric juice secretion and enzyme production - Helping treat Small Intestinal Bacterial Overgrowth (SIBO) - Managing digestive discomfort, bloating, and IBS symptoms ## Anti-inflammatory and Antioxidant Effects The oil provides significant protective benefits through: - Powerful antioxidant activity that fights free radicals - Reduction of inflammatory markers in the body - Protection against oxidative stress-related conditions ## Respiratory Support It aids respiratory health by: - Loosening mucus and phlegm - Suppressing coughs and throat irritation - Supporting overall respiratory tract function ## Additional Benefits **Skin Health** - Improves conditions like psoriasis, acne, and eczema - Supports wound healing through antibacterial action - Provides anti-aging benefits through antioxidant properties **Cardiovascular Health** Studies show oregano oil may help: - Reduce LDL (bad) cholesterol levels - Support overall heart health **Pain Management** The oil demonstrates effectiveness in: - Reducing inflammation-related pain - Managing muscle discomfort - Providing topical pain relief ## Safety Note While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications. @ b17fccdf:b7211155
2025-01-21 17:02:21The past 26 August, Tor [introduced officially](https://blog.torproject.org/introducing-proof-of-work-defense-for-onion-services/) a proof-of-work (PoW) defense for onion services designed to prioritize verified network traffic as a deterrent against denial of service (DoS) attacks. ~ > This feature at the moment, is [deactivate by default](https://gitlab.torproject.org/tpo/core/tor/-/blob/main/doc/man/tor.1.txt#L3117), so you need to follow these steps to activate this on a MiniBolt node: * Make sure you have the latest version of Tor installed, at the time of writing this post, which is v0.4.8.6. Check your current version by typing ``` tor --version ``` **Example** of expected output: ``` Tor version 0.4.8.6. This build of Tor is covered by the GNU General Public License (https://www.gnu.org/licenses/gpl-3.0.en.html) Tor is running on Linux with Libevent 2.1.12-stable, OpenSSL 3.0.9, Zlib 1.2.13, Liblzma 5.4.1, Libzstd N/A and Glibc 2.36 as libc. Tor compiled with GCC version 12.2.0 ``` ~ > If you have v0.4.8.X, you are **OK**, if not, type `sudo apt update && sudo apt upgrade` and confirm to update. * Basic PoW support can be checked by running this command: ``` tor --list-modules ``` Expected output: ``` relay: yes dirauth: yes dircache: yes pow: **yes** ``` ~ > If you have `pow: yes`, you are **OK** * Now go to the torrc file of your MiniBolt and add the parameter to enable PoW for each hidden service added ``` sudo nano /etc/tor/torrc ``` Example: ``` # Hidden Service BTC RPC Explorer HiddenServiceDir /var/lib/tor/hidden_service_btcrpcexplorer/ HiddenServiceVersion 3 HiddenServicePoWDefensesEnabled 1 HiddenServicePort 80 127.0.0.1:3002 ``` ~ > Bitcoin Core and LND use the Tor control port to automatically create the hidden service, requiring no action from the user. We have submitted a feature request in the official GitHub repositories to explore the need for the integration of Tor's PoW defense into the automatic creation process of the hidden service. You can follow them at the following links: * Bitcoin Core: https://github.com/lightningnetwork/lnd/issues/8002 * LND: https://github.com/bitcoin/bitcoin/issues/28499 --- More info: * https://blog.torproject.org/introducing-proof-of-work-defense-for-onion-services/ * https://gitlab.torproject.org/tpo/onion-services/onion-support/-/wikis/Documentation/PoW-FAQ --- Enjoy it MiniBolter! 💙
@ b17fccdf:b7211155
2025-01-21 17:02:21The past 26 August, Tor [introduced officially](https://blog.torproject.org/introducing-proof-of-work-defense-for-onion-services/) a proof-of-work (PoW) defense for onion services designed to prioritize verified network traffic as a deterrent against denial of service (DoS) attacks. ~ > This feature at the moment, is [deactivate by default](https://gitlab.torproject.org/tpo/core/tor/-/blob/main/doc/man/tor.1.txt#L3117), so you need to follow these steps to activate this on a MiniBolt node: * Make sure you have the latest version of Tor installed, at the time of writing this post, which is v0.4.8.6. Check your current version by typing ``` tor --version ``` **Example** of expected output: ``` Tor version 0.4.8.6. This build of Tor is covered by the GNU General Public License (https://www.gnu.org/licenses/gpl-3.0.en.html) Tor is running on Linux with Libevent 2.1.12-stable, OpenSSL 3.0.9, Zlib 1.2.13, Liblzma 5.4.1, Libzstd N/A and Glibc 2.36 as libc. Tor compiled with GCC version 12.2.0 ``` ~ > If you have v0.4.8.X, you are **OK**, if not, type `sudo apt update && sudo apt upgrade` and confirm to update. * Basic PoW support can be checked by running this command: ``` tor --list-modules ``` Expected output: ``` relay: yes dirauth: yes dircache: yes pow: **yes** ``` ~ > If you have `pow: yes`, you are **OK** * Now go to the torrc file of your MiniBolt and add the parameter to enable PoW for each hidden service added ``` sudo nano /etc/tor/torrc ``` Example: ``` # Hidden Service BTC RPC Explorer HiddenServiceDir /var/lib/tor/hidden_service_btcrpcexplorer/ HiddenServiceVersion 3 HiddenServicePoWDefensesEnabled 1 HiddenServicePort 80 127.0.0.1:3002 ``` ~ > Bitcoin Core and LND use the Tor control port to automatically create the hidden service, requiring no action from the user. We have submitted a feature request in the official GitHub repositories to explore the need for the integration of Tor's PoW defense into the automatic creation process of the hidden service. You can follow them at the following links: * Bitcoin Core: https://github.com/lightningnetwork/lnd/issues/8002 * LND: https://github.com/bitcoin/bitcoin/issues/28499 --- More info: * https://blog.torproject.org/introducing-proof-of-work-defense-for-onion-services/ * https://gitlab.torproject.org/tpo/onion-services/onion-support/-/wikis/Documentation/PoW-FAQ --- Enjoy it MiniBolter! 💙