-
 @ f5369849:f34119a0
2025-04-16 14:13:12
@ f5369849:f34119a0
2025-04-16 14:13:12Hackathon Summary
The AI Hackathon, hosted by SUCI Blockchain Hub and sponsored by CodeX, took place in Ho Chi Minh City, Vietnam, from March 7-9, 2025. This in-person event saw participation from 42 developers who created 12 projects, addressing Real-World Asset integration and AI agent development with a practical focus.
The hackathon distributed a total prize pool of $15,000, allocated in USDT and CDX tokens. The first-place winner was awarded $4,000 USDT and 2,000 CDX tokens, along with travel and accommodation to the upcoming COTI Foundation Hackathon in Thailand. The second and third place winners received $3,000 and $2,000 USDT, respectively, along with CDX tokens.
Special track-specific prizes were awarded in categories including Best AI Agent, Best No-Code Solution, and Best Real-World Application, each receiving $1,000 USDT and 500 CDX tokens. Additional awards recognized innovative AI use, cross-industry solutions, and community impact.
The event facilitated networking, learning, and collaborative innovation, demonstrating the growing overlap between AI and blockchain technologies.
Hackathon Winners
The AI Hackathon 2025 produced notable accomplishments, highlighting technical innovation and creativity across various fields. Over 48 hours, participants collaborated and problem-solved intensively, resulting in distinguished projects evaluated under three prize categories: Main Prizes, Track-Specific Prizes, and Special Prizes.
Main Prize Winners
The top three projects stood out for their innovation and implementation:
- VocakeX: This Web3 edtech platform uses gamification and AI to enhance learning, integrating AI-driven modules with gamified elements to improve educational engagement and retention.
- StudyVerse: An AI platform offering personalized well-being advice and study guidance by analyzing student emotions, aiming to enhance education through emotional recognition and adaptive feedback.
- VaultAI: An AI-powered crypto wallet designed for sophisticated asset management and DeFi insights, utilizing analytics and machine learning to optimize financial decisions.
Track-Specific Prize Winners
Projects were recognized for achievements in AI Agents, No-Code Solutions, and Real-World Applications:
- CryptoMentor: A smart chatbot aiding new investors in learning and transacting in crypto, offering real-time API integration for reliable assistance.
- VaultAI
- Scholar AI: An AI tool that assists individuals in making informed study-abroad decisions by recommending tailored educational and financial opportunities through data analysis.
Special Prize Winners
These awards spotlighted projects with potential in innovation, cross-industry use, and community impact:
- StudyVerse
- TourRecommendation: An AI tool for tourists to find reliable dining and accommodation through blockchain-fueled transparency, enhancing trust in transactions.
- Buildlink: Simplifies blockchain interactions with AI, offering user-friendly swapping and staking on the NEAR blockchain to improve accessibility for new users.
The hackathon emphasized AI's capability to address complex issues and provide impactful solutions across domains. Additional details on all projects can be found at the Dorahacks AI Hackathon.
About the Organizer
SUCI BLOCKCHAIN HUB
SUCI Blockchain Hub is dedicated to the development and implementation of blockchain technology. The organization is recognized for advancing secure, decentralized solutions in various industries and has contributed to significant blockchain projects. Through research and development, SUCI Blockchain Hub fosters innovation and collaborates with industry leaders to enhance blockchain's applications, promoting accessibility and transparency in digital transactions. Currently, the organization's mission focuses on expanding blockchain integration to provide efficient, secure solutions for businesses and individuals.
-
 @ f5369849:f34119a0
2025-04-16 14:09:00
@ f5369849:f34119a0
2025-04-16 14:09:00Hackathon Summary
The Privacy and Verifiability Hackathon, organized by the Blockchain Student Association at EPFL, was held from March 8 to March 9, 2023 at the École Polytechnique de Lausanne, Switzerland. The event drew 36 registered developers who submitted 23 approved projects within the 26-hour challenge timeframe. Participants were tasked with developing solutions for privacy and verifiability in blockchain technology, with sponsorship from Mina, the Hedera Hashgraph Association, and Hylé. A total prize pool of $15,000 was offered.
Notable achievements included innovations in privacy-enhancing methods and verifiable blockchain solutions. Projects were assessed based on criteria such as innovation, technical execution, and effectiveness in addressing privacy and verifiability issues. The diverse solutions presented highlighted originality and practical applications within blockchain domains.
The hackathon fostered collaboration and creativity among students, professionals, and enthusiasts, advancing discussions on privacy and verifiable blockchain technologies. The event emphasized the potential of decentralized solutions to tackle privacy challenges, further affirming the community's commitment to advancing blockchain innovation.
Hackathon Winners
The Privacy and Verifiability Hackathon culminated with over 25 projects competing for a $15,000 prize pool. It showcased innovative solutions across three categories, emphasizing advancements in privacy and verification technologies.
Mina Prize Winners
- Mina Cash: Utilizes zero-knowledge proofs on the Mina Protocol for anonymous payment transactions, ensuring on-chain proofs and off-chain privacy.
- zkPetitions: A decentralized application employing zero-knowledge proofs to protect privacy and data integrity in petition handling.
- ZKribble.io: A game using zero-knowledge proofs to secure secret words in a drawing and guessing context.
- Aether ticket: Platform for ticket verification integrating Mina Protocol for secure, private validation with zero-knowledge proofs.
- Hush tag: Decentralized ticketing system using the Mina Protocol for secure and private ticket generation and validation.
The Hedera Hashgraph Association Prize Winners
- AtlasID: Implements privacy-centric identity verification using React, Express, and SD-JWT VC technology.
- donate.fun: Enhances humanitarian aid transparency and security through blockchain and identity verification.
- Geotrust: A web application for geocaching, featuring location creation and robust user verification.
- Hedemon: Converts physical collectibles into NFTs using Hedera blockchain to ensure verifiable authenticity and privacy.
Hylé Prize Winners
- Sthylé - image verification: A blockchain-powered platform for verifying image authenticity and management.
- zkIA: Focuses on zero-knowledge proofs in AI applications, though specific technical details are not provided.
- CipherSocial: Connects users based on interests via a decentralized platform using cryptography and blockchain for privacy.
- Plethora: A tool for creating AI agents with zero-knowledge proofs for private, verifiable task completion.
For a complete list of projects and further details, visit the hackathon page at dorahacks.io.
About the Organizer
Blockchain Student Association
The Blockchain Student Association aims to educate and engage students in the field of blockchain technology in Switzerland. Known for its expertise in blockchain systems and applications, the organization actively hosts seminars and workshops to enhance members' technical understanding. It has collaborated with industry leaders on projects focusing on innovative blockchain solutions. The group's mission is to foster a knowledgeable community that explores practical blockchain applications and advances technological literacy in this rapidly evolving field.
-
 @ f5369849:f34119a0
2025-04-16 13:57:15
@ f5369849:f34119a0
2025-04-16 13:57:15Hackathon Summary
The HackCanada hackathon brought together innovators, coders, designers, and problem-solvers to tackle pressing challenges in Canada, such as healthcare accessibility, environmental sustainability, digital infrastructure, and economic disparities. The event saw participation from 188 developers who contributed 89 unique projects from the hackathon at Wilfrid Laurier University, Ontario, Canada.
Among these projects were initiatives aimed at enhancing healthcare systems through technology, improving digital infrastructure in remote communities, and employing innovative methods to reduce environmental footprints. The hackathon served as a platform for collaborative creation, enabling fresh ideas and practical solutions that align with its objectives of promoting tangible benefits and inspiring change.
Overall, HackCanada facilitated a dynamic environment for collaboration and innovation, contributing to the development of technologies aimed at improving Canadians' quality of life. The event acted as a catalyst for community-driven innovation, encouraging continued efforts toward a more inclusive and sustainable future.
Hackathon Winners
First Place Overall Prize Winners
- Phone-a-Fraud - An AI-driven system designed to detect phone scams in real-time, with a focus on privacy and fraud alert mechanisms to protect vulnerable individuals.
Second Place Overall Prize Winners
- StickTator - A USB device that leverages natural language processing for voice-controlled computer management, simplifying complex system configurations.
Third Place Overall Prize Winners
- Omnivim - Software that integrates Vim motions across applications to enhance productivity.
Best Solo Hack Prize Winners
Best Orkes Hack Prize Winners
- Recipeit - A project focused on recipes; further details are unavailable.
Best ICP Hack Prize Winners
- DigiTag - A blockchain application that secures transactions of luxury items using NFTs and the Internet Computer Protocol for fraud prevention.
- LandLocks - A platform that manages land records as NFTs utilizing blockchain technology.
SPUR Innovation Fund: Best Use of AI, Web3, or Quantum Technology Prize Winners
First Place
- Beaver Breach - Analysis tool for US tariff impacts on products, providing cost-reducing alternatives through Canadian suppliers.
Second Place
- Canify - Blockchain Rewards - Encourages support for Canadian products with blockchain-based rewards and government incentives.
Autonomous Agent Bounty Track Prize Winners
First Place
- ChainMail - A web3-based email application that enhances security and enables cross-blockchain communication.
Second Place
Third Place
- Roast My Wallet - A web application that generates AI-driven humor based on users' crypto wallets and personalities.
- Zap - Facilitates crypto application in daily life with fee-free transactions.
- Carbon Chain - Blockchain platform converting carbon reductions into tradable assets, verified by AI.
Best Developer Tool Prize Winners
Best High School Hack Prize Winners
- NaloxNow - Mobile app aimed at combating the opioid crisis through real-time naloxone access, emergency navigation, and AI-driven overdose response.
Most Useless Hack Prize Winners
- UselessGPT - An interactive app utilizing Google's Gemini API to produce nonsensical, entertainment-focused outputs.
Best AI App Prize Winners
- frij.io - A smart app that manages household inventory using AI to optimize grocery lists and reduce food waste.
Build With AI: Google Track Prize Winners
- Best Use of Gemini AI or Gemini API, Best Use of Google Cloud Platform, and Best Integration of Google Toolkit:
- Sinker - An AI-powered cybersecurity platform training employees to identify phishing threats in communication channels.
- FrostByte - Project details are unavailable.
- Flock Street - An interactive application providing stock market insights using real-time data and speech technology.
Best Laurier STEM Publishing Society Prize Winners
- SockSensei - Mobile app offering sock recommendations by detecting user mood.
For a complete list of projects, visit this link.
About the Organizer
Hack Canada
Hack Canada is recognized for hosting national hackathons and workshops designed to enhance knowledge of digital security. Through its dynamic hackathons, Hack Canada has inspired numerous projects contributing to the technological landscape.
-
 @ 1bc70a01:24f6a411
2025-04-16 13:53:00
@ 1bc70a01:24f6a411
2025-04-16 13:53:00I've been meaning to dogfood my own vibe project for a while so this feels like a good opportunity to use Untype to publish this update and reflect on my vibe coding journey.
New Untype Update
As I write this, I found it a bit annoying dealing with one of the latest features, so I'll need to make some changes right after I'm done. Nonetheless, here are some exciting developments in the Untype article composer:
-
Added inline AI helper! Now you can highlight text and perform all sorts of things like fix grammar, re-write in different styles, and all sorts of other things. This is a bit annoying at the moment because it takes over the other editing functions and I need to fix the UX.
-
Added pushing articles to DMs! This option, when enabled, will send the article to all the subscribers via a NIP-44 DM. (No client has implemented the subscription method yet so technically it won’t work, until one does. I may add this to nrss.app) Also, I have not tested this so it could be broken… will test eventually!
- Added word counts
- Added ability to export as markdown, export as PDF, print.
The biggest flaw I have already discovered is how "I" implemented the highlight functionality. Right now when you highlight some text it automatically pops up the AI helper menu and this makes for an annoying time trying to make any changes to text. I wanted to change this to show a floating clickable icon instead, but for some reason the bot is having a difficult time updating the code to this desired UX.
Speaking of difficult times, it's probably a good idea to reflect a bit upon my vibe coding journey.
Vibe Coding Nostr Projects
First, I think it's important to add some context around my recent batch of nostr vibe projects. I am working on them mostly at night and occasionally on weekends in between park runs with kids, grocery shopping and just bumming around the house. People who see buggy code or less than desired UX should understand that I am not spending days coding this stuff. Some apps are literally as simple as typing one prompt!
That said, its pretty clear by now that one prompt cannot produce a highly polished product. This is why I decided to limit my number of project to a handful that I really wish existed, and slowly update them over time - fixing bugs, adding new features in hopes of making them the best tools - not only on nostr but the internet in general. As you can imagine this is not a small task, especially for sporadic vibe coding.
Fighting the bot
One of my biggest challenges so far besides having very limited time is getting the bot to do what I want it to do. I guess if you've done any vibe coding at all you're probably familiar with what I'm trying to say. You prompt one thing and get a hallucinated response, or worse, a complete mess out the other end that undoes most of the progress you've made. Once the initial thing is created, which barely took any time, now you're faced with making it work a certain way. This is where the challenges arise.
Here's a brief list of issues I've faced when vibe-coding with various tools:
1. Runaway expenses - tools like Cline tend to do a better job directly in VSCode, but they can also add up dramatically. Before leaning into v0 (which is where I do most of my vibe coding now), I would often melt through $10 credit purchases faster than I could get a decent feature out. It was not uncommon for me to spend $20-30 on a weekend just trying to debug a handful of issues. Naturally, I did not wish to pay these fees so I searched for alternatives.
2. File duplication - occasionally, seemingly out of nowhere, the bot will duplicate files by creating an entire new copy and attached "-fixed" to the file name. Clearly, I'm not asking for duplicate files, I just want it to fix the existing file, but it does happen and it's super annoying. Then you are left telling it which version to keep and which one to delete, and sometimes you have to be very precise or it'll delete the wrong thing and you have to roll back to a previous working version.
3. Code duplication - similar to file duplication, occasionally the bot will duplicate code and do things in the most unintuitive way imaginable. This often results in loops and crashes that can take many refreshes just to revert back to a working state, and many more prompts to avoid the duplication entirely - something a seasoned dev never has to deal with (or so I imagine).
4. Misinterpreting your request - occasionally the bot will do something you didn't ask for because it took your request quite literally. This tends to happen when I give it very specific prompts that are targeted at fixing one very specific thing. I've noticed the bots tend to do better with vague asks - hence a pretty good result on the initial prompt.
5. Doing things inefficiently, without considering smarter approaches - this one is the most painful of vibe coding issues. As a person who may not be familiar with some of the smarter ways of handling development, you rely on the bot to do the right thing. But, when the bot does something horribly inefficiently and you are non-the-wiser, it can be tough to diagnose the issue. I often fight myself asking the bot "is this really the best way to handle things? Can't we ... / shouldn't we .../ isn't this supposed to..." etc. I guess one of the nice side effects of this annoyance is being able to prompt better. I learn that I should ask the bot to reflect on its own code more often and seek ways to do things more simply.
A combination of the above, or total chaos - this is a category where all hell breaks loose and you're trying to put out one fire after another. Fix one bug, only to see 10 more pop up. Fix those, to see 10 more and so on. I guess this may sound like typical development, but the bot amplifies issues by acting totally irrationally. This is typically when I will revert to a previous save point and just undo everything, often losing a lot of progress.
Lessons Learned
If I had to give my earlier self some tips on how to be a smarter vibe coder, here's how I'd summarize them:
-
Fork often - in v0 I now fork for any new major feature I'd like to add (such as the AI assistant).
-
Use targeting tools - in v0 you can select elements and describe how you wish to edit them.
-
Refactor often - keeping the code more manageable speeds up the process. Since the bot will go through the entire file, even if it only makes one small change, it's best to keep the files small and refactoring achieves that.
I guess the biggest lesson someone might point out is just to stop vibe coding. It may be easier to learn proper development and do things right. For me it has been a spare time hobby (one that I will admit is taking more of my extra time than I'd like). I don't really have the time to learn proper development. I feel like I've learned a lot just bossing the bot around and have learned a bunch of things in the process. That's not to say that I never will, but for the moment being my heart is still mostly in design. I haven't shared much of anything I have designed recently - mostly so I can remain speaking more freely without it rubbing off on my work.
I'll go ahead and try to publish this to see if it actually works 😂. Here goes nothing... (oh, I guess I could use the latest feature to export as markdown so I don't lose any progress! Yay!
-
-
 @ 5d4b6c8d:8a1c1ee3
2025-04-16 13:27:53
@ 5d4b6c8d:8a1c1ee3
2025-04-16 13:27:53https://primal.net/e/nevent1qvzqqqqqqypzqntcggz30qhq60ltqdx32zku9d46unhrkjtcv7fml7jx3dh4h94nqqszw6rqxppmm48pvvc5pz4q74r7qvsgl8tzwfgp3kqg82jw04t2n3q2nrlqh
Get used to and comfortable with being responsible for your own wellbeing.
originally posted at https://stacker.news/items/945039
-
 @ f5369849:f34119a0
2025-04-16 13:13:21
@ f5369849:f34119a0
2025-04-16 13:13:21Hackathon Overview
The Eolas x Algo: Agent Skills Hackathon was held online, aiming to boost the CreatorBid ecosystem by advancing agent skills. The event involved 58 developers and culminated in the approval of 36 projects. Uniquely, this hackathon allowed CreatorBid agents to directly commission needed skills, removing traditional intermediaries.
Participants competed in two main tracks. The Bounty Track aimed to solve specific problems identified by agents, while the Best Skills Track rewarded exemplary projects. Financial backing was provided by Eolas, Algo, Shogun, AION, and various individual agents.
Projects developed during the hackathon were integrated directly into the Olas Mech Marketplace, promoting live deployment and offering developers rewards through the OLAS system. Top agents, including Agent Algo and Eolas, emphasized the hackathon's importance in promoting agent innovation.
The event concluded on March 20. Judges from CreatorBid staff and agents assessed entries based on innovation and their impact within the ecosystem.
Hackathon Winners
The following section details the accomplishments and awards from the first-ever agent-sponsored hackathon, highlighting 37 projects across various categories.
Best Agent Skill Track Prize Winners
- Agent Toolbox: A suite designed to enhance AI agents with capabilities like trend discovery, dynamic function generation, and task orchestration.
- GridTrade Agent: Facilitates automated trading pair selection and grid trading parameter optimization through market and volatility analysis.
- Polytrader: An AI-based trading assistant that streamlines research, data analysis, and trade execution in Polymarket.
Main Prize Pool Winners
- sentimentX: Offers AI-driven security monitoring for MultiversX blockchain smart contracts by detecting vulnerabilities.
- Brainiac_AI: A platform for optimizing DeFi strategies with on-chain analysis alongside non-custodial wallet integration.
- framew0rk: Simplifies DeFi yield optimization using an AI strategy assistant linked to DeFi protocols.
- MythosCraft: AI Storytelling Suite: Allows for the creation of customizable storytelling content using AI.
- QuanTrade-X: Provides AI-powered analytics and trading signals for cryptocurrency trading.
- ComicVerse AI: Generates comics using AI for script and image creation based on user input.
- EOLAS - Submit your own skill: Portfolio Allocation Skill: Uses AI and Modern Portfolio Theory to optimize cryptocurrency portfolios.
- SonicBo: An AI agent on WhatsApp that facilitates blockchain transactions.
- 👽Zeta Comic Generator👽: Converts text prompts into AI-generated comic strips, complete with scripts and character expressions.
- Grid Trading Analyzer Skill: A Python tool for advanced analysis to identify optimal cryptocurrency grid trading pairs.
- Trump news Reporter: An AI tool for real-time monitoring and reporting of Trump-related news with customizable filters.
- NFT Appraisal skill: Creates AI agents for NFT appraisals.
- AI-Powered Dynamic Skill Selector (DSS): Utilizes a Multi-Armed Bandit strategy for dynamic AI model optimization.
- CrypTweet: An AI trading bot that uses Twitter sentiment to inform crypto trading decisions.
- AI Trump News Agent: Monitors and analyzes Trump-related news with customizable report tones.
- TrumpTracker-AI: Compiles and summarizes Trump-related news, generating memes from popular headlines.
- Rigger-: Turns natural language into SQL queries, easing database access for non-technical users.
- TNS: Tracks Trump-related news using NLP and offers diverse reporting styles.
- Bob Roast Machine: An AI platform for crafting comedic roasts, jokes, and memes.
- Agent 47: A Telegram bot delivering political news with AI-generated memes and fact-checking.
Skill Coordination & Optimization Prize Winner
Build Skills for Enhancing Data Access to CB Agents Prize Winner
World-Building & Lore Promotion Skills Prize Winner
Polymarket Trading Bots Prize Winner
For a comprehensive list of projects, visit DoraHacks.
About the Organizer
Eolas
Eolas is a key player in technology and blockchain, noted for its blockchain solutions enhancing transactional transparency. The organization continues its focus on blockchain research and development, tackling industry challenges to drive future progress.
-
 @ edeb837b:ac664163
2025-04-16 12:59:09
@ edeb837b:ac664163
2025-04-16 12:59:09If you’ve spent any time around stock trading communities, chances are you’ve heard the name Webull pop up more than once. It’s not just another brokerage app—it’s one of the go-to platforms for retail traders across the globe. But what exactly is Webull? Why do so many individual traders prefer it over other platforms? And how does NVSTly take its capabilities even further?
Let’s break it all down.
What Is Webull?
Webull is a commission-free trading app that allows users to trade stocks, ETFs, options, and cryptocurrencies from their phones or desktop. Launched in 2017, it quickly gained popularity for its sleek interface, real-time data, and powerful tools—all without the traditional fees associated with many brokerage platforms.
While it’s often compared to Robinhood, Webull caters more to active traders and those who want slightly more advanced tools without the complexity (or costs) of institutional-level platforms.
What Can You Do on Webull?
Webull offers a full suite of features for modern traders:
- Commission-free trading for stocks, options, ETFs, and crypto
- Extended trading hours (premarket and after-hours)
- In-depth charting tools with technical indicators
- Fractional shares trading to invest with any dollar amount
- Paper trading for practice without real money
- Level 2 market data (Nasdaq TotalView, subscription-based)
- Custom alerts and watchlists
- Community feed for trade ideas and discussions
Whether you’re a beginner trying to learn the ropes or an experienced trader managing multiple positions daily, Webull is designed to give you an edge.
Why Retail Traders Prefer Webull Over Other Brokers
Here are some reasons why Webull has become a fan favorite among retail traders:
✅ Advanced Tools, Simple UI
Unlike many traditional brokers with clunky interfaces, Webull balances powerful tools with a user-friendly design. You get access to real-time quotes, charting with dozens of indicators, and customizable layouts—all wrapped in a clean, modern app.
✅ Free Options Trading
While some platforms charge per contract or per trade for options, Webull offers commission-free options trading, which is a huge win for active options traders.
✅ No Account Minimums
New traders can get started with as little (or as much) money as they want. There are no minimum deposit requirements for standard cash or margin accounts.
✅ Fractional Shares
Webull lets users invest in fractional shares, meaning you don’t need to buy an entire share of high-priced stocks like Amazon or Tesla. You can invest as little as $5 into a stock, making it easier to build a diversified portfolio with any budget.
✅ Paper Trading
Webull gives users a way to test strategies in a simulated environment, which is perfect for learning without risking real money.
✅ Mobile & Desktop Support
Webull’s mobile app is robust, but the desktop version is just as powerful—great for traders who prefer multi-screen setups or deeper analysis.
Webull Pros & Cons
✅ Pros
- $0 commissions on stocks, options, ETFs, and crypto
- Clean and intuitive interface
- Real-time data and news
- Built-in paper trading
- Fractional shares
- Support for extended hours trading
- Level 2 market data available
⚠️ Cons
- No mutual funds
- Webull uses a high spread for crypto trading
- Slight learning curve for beginners
How NVSTly Supercharges Your Webull Experience
Webull is powerful on its own—but when integrated with NVSTly, it becomes next-level.
NVSTly is the fastest-growing social trading app, where traders can automatically track, share, and analyze their trades, all in one place. Thanks to deep Webull integration, you can now connect your Webull account to NVSTly in seconds.
🔗 Connect in Seconds with a QR Code
Linking your Webull account is as simple as scanning a QR code inside your NVSTly account settings using the Webull mobile app. That’s it—your trades are now synced automatically.
💼 What You Get with NVSTly + Webull
- Auto-tracked trades — No more manual logging or screenshots
- Real-time trade sharing — Followers see your trades as they happen
- Performance analytics — Gain insights into your win rate, risk/reward, and more
- Automate your trade signals — Save time and help followers catch entries earlier, closer to your price
- Trade history dashboards — View and share detailed stats for your trades, with visual breakdowns
- Daily/Weekly/Monthly Recaps — Get beautifully designed trade summaries sent straight to your Discord or social profiles
Whether you’re a solo trader or part of a larger trading community, NVSTly makes it ridiculously easy to share your journey, learn from others, and improve your performance—all while staying 100% focused on the markets.
Final Thoughts
Webull has earned its spot as a top-tier brokerage app for retail traders, offering a powerful platform with zero commissions and high-quality tools. When paired with NVSTly, your trading becomes smarter and more connected—automating the way your trades are tracked, shared, and analyzed, so you can focus on the markets while NVSTly handles the rest.
If you’re a Webull user and haven’t connected to NVSTly yet, now’s the time. Your trading deserves more than just a broker—it deserves a platform built to grow with you.
Ready to level up your Webull trading?
➡️ Sign in to NVSTly, go to Brokerages & Exchanges in your account settings, click Connect next to Webull, and follow the QR code instructions to link your account in seconds.Available on web, iOS, Android, & fully integrated with Discord through a unique bot – the only of its kind!
-
 @ 7d33ba57:1b82db35
2025-04-16 12:52:15
@ 7d33ba57:1b82db35
2025-04-16 12:52:15Addo Elephant National Park is a premier wildlife destination in South Africa's Eastern Cape, located approximately 70 km from Gqeberha (formerly Port Elizabeth). Established in 1931 to protect a small group of elephants, the park has since expanded to become the third-largest national park in the country, encompassing diverse landscapes from the Karoo to the coast.
🐘 Wildlife Highlights
-
Elephants:Home to over 600 elephants, the park offers exceptional opportunities to observe these majestic creatures in their natural habitat
-
Big Five:In addition to elephants, visitors can encounter lions, leopards, buffaloes, and black rhinos.
-
Big Seven:The park's marine section includes great white sharks and southern right whales, making it one of the few places boasting the "Big Seven.
-
Other Species:The park hosts a variety of wildlife, including zebras, antelopes, meerkats, and over 400 bird species.
🚙 Activities
-
Self-Drive Safaris Explore the park at your own pace on well-maintained road.
-
Guided Game Drives Join expert-led tours for in-depth wildlife viewing experience.
-
Hiking Trails Discover the park's diverse flora and fauna on designated walking path.
-
Bird Watching With a rich avian population, the park is a haven for bird enthusiast.
-
Picnic Spots Enjoy meals amidst nature at designated picnic area.
🏨 Accommodation
The park offers various lodging options, including rest camps and luxury lodges like Camp Figtree, catering to different preferences and budges.
🌿 Visitor Tips
-
*Malaria-Free: The park is located in a malaria-free zone, making it suitable for families and travelers of all aes.
-
*Accessibility: Easily reachable from Gqeberha, it's an excellent addition to a Garden Route itinerry.
-
*Conservation Efforts: The park plays a crucial role in preserving South Africa's biodiversity, offering visitors a chance to support and learn about conservation initiaties.
For more information and to plan your visit, you can explore the official SANParks website.
-
-
 @ 06639a38:655f8f71
2025-04-16 12:11:31
@ 06639a38:655f8f71
2025-04-16 12:11:31Finally there is a release (1.7.0) for Nostr-PHP with a full NIP-19 integration. Here is an example file with some snippets to how it works to encode and decode bech32 encoded entities:
- https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip19-bech32-decoded-entities.php
- https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip19-bech32-encoded-entities.php
Now merge request #68 (and issues #74, #64 are closed) is finally merged which I opened in October 2024.
Next up is:
- Create documentation how to use NIP-19 with the library on https://nostr-php.dev
- Create documentation how to use NIP-04 and NIP-44 with the library on https://nostr-php.dev
- Work out a proof-of-concept with the revolt/event-loop package to create concurrent async requests with websocket connections
-
 @ 4cebd4f5:0ac3ed15
2025-04-16 11:22:05
@ 4cebd4f5:0ac3ed15
2025-04-16 11:22:05ElleHacks 2025 – sự kiện hackathon nổi bật tại Canada, diễn ra từ ngày 14–16/2/2025 với mục tiêu thúc đẩy đa dạng và hòa nhập trong lĩnh vực STEM (Khoa học, Công nghệ, Kỹ thuật, Toán học). Sự kiện thu hút 195 lập trình viên sinh viên (tập trung vào nữ giới và nhóm phi nhị nguyên), với 72 dự án được phê duyệt. ElleHacks 2025 hướng đến người mới bắt đầu, trang bị công cụ để đề xuất giải pháp kỹ thuật sáng tạo cho thách thức toàn cầu thông qua hợp tác nhóm.
Người tham gia được trải nghiệm workshop, kết nối với chuyên gia và nhà tuyển dụng, đồng thời nâng cao kỹ năng để thể hiện tư duy sáng tạo. Dù thử thách cụ thể chỉ được tiết lộ trong sự kiện, hackathon tập trung vào vấn đề thực tế, khuyến khích ứng dụng kỹ năng giải quyết vấn đề vào giải pháp có tác động.
Lễ bế mạc bao gồm phần thuyết trình dự án được chấm điểm ngay sau hạn nộp. ElleHacks 2025 không chỉ nhấn mạnh vai trò của đa dạng trong STEM mà còn tạo nền tảng ý nghĩa để sinh viên nữ và phi nhị nguyên đóng góp qua dự án công nghệ.
Các dự án đoạt giải
ElleHacks 2025 vinh danh dự án xuất sắc theo nhiều hạng mục:
Best Use of ElleHacks Theme Prize Winners
- Memora {Old Age}: Ứng dụng cộng đồng hỗ trợ bệnh nhân Alzheimer qua nhận diện ký ức và quản lý thuốc, kết hợp AI và IoT.
- KareBear: Trợ lý ảo AI giúp trẻ mắc chứng tự kỷ học hỏi và biểu đạt cảm xúc.
- talktome: Nền tảng mô phỏng cung cấp chiến lược cá nhân hóa, hỗ trợ phụ huynh giao tiếp với thanh thiếu niên.
Best Use of Hardware Prize Winner
Best Use of EA Data Prize Winner
- Connect Beyond Barriers: Autism Care: Nền tảng AI hỗ trợ trẻ tự kỷ nữ và phụ huynh, tích hợp chatbot và định vị chuyên gia.
Best Use of Cybersecurity Prize Winner
- Lynx: Công cụ phân tích dấu chân số (digital footprint), đề xuất quản lý danh tiếng.
Best Use of Wasp Prize Winner
- NetNanny: Tiện ích trình duyệt và web app sử dụng AI bảo vệ trẻ khỏi rủi ro trực tuyến.
Best Use of Streamlit Prize Winner
- CyberQueen: Web app giáo dục an ninh mạng cho nữ trẻ qua chatbot AI và câu đố.
Best AI Application Built with Cloudflare Prize Winner
- CareOn: Ứng dụng AI đảm bảo an toàn cho người già bằng phát hiện chuyển động và cảnh báo thông minh.
Best Domain Name from GoDaddy Registry Prize Winner
- Greener Than You Think: Trang web tương tác giúp thanh thiếu niên điều chỉnh cảm xúc qua kiểm tra tâm trạng và quản lý vườn ảo.
Best Use of Gen AI Prize Winner
- Talky: Ứng dụng trị liệu ngôn ngữ dạng game hóa cho trẻ gặp khó khăn phát âm, tùy chỉnh thử thách bằng AI.
Chi tiết các dự án tại trang sự kiện.
Về Nhà tổ chức
ElleHacks
ElleHacks cam kết thúc đẩy đa dạng và hòa nhập trong ngành công nghệ, đặc biệt trao quyền cho nữ giới. Tổ chức nổi tiếng với hackathon thường niên, nơi kết nối người tham gia phát triển dự án sáng tạo, đồng thời hỗ trợ nâng cao kỹ năng và mạng lưới quan hệ. ElleHacks tập trung vào giáo dục và xây dựng cộng đồng, khuyến khích hợp tác đa ngành. Với sứ mệnh nuôi dưỡng tài năng, ElleHacks mở rộng cơ hội cho nhóm thiểu số trong công nghệ, trở thành chất xúc tác cho thay đổi tích cực trong ngành.
-
 @ 4cebd4f5:0ac3ed15
2025-04-16 11:07:39
@ 4cebd4f5:0ac3ed15
2025-04-16 11:07:39Hackathon@WEF 2025 diễn ra từ ngày 21–23/1/2025 tại Davos, Thụy Sĩ, thu hút 23 lập trình viên đăng ký với 7 dự án được phê duyệt. Sự kiện nhằm giải quyết các thách thức toàn cầu thông qua AI (trí tuệ nhân tạo), khoa học dữ liệu (data science) và công nghệ tiên tiến.
Người tham gia làm việc theo nhóm tại Lab42, Innovation Center Davos hoặc từ xa, tập trung xây dựng giải pháp có tính ứng dụng thực tế. Ban tổ chức cung cấp hướng dẫn từ chuyên gia và phân tích xu hướng công nghệ để hỗ trợ phát triển kỹ năng.
Điểm nhấn của sự kiện là DIGITAL LOUNGE@WEF – nền tảng kết nối lập trình viên với CEO, quan chức chính phủ, doanh nhân và lãnh đạo tư tưởng. Đây là cơ hội để các đội trình bày dự án trước đối tượng uy tín, mở rộng tầm ảnh hưởng và thăng tiến sự nghiệp.
Hackathon diễn ra tại dãy Alps Thụy Sĩ, bao gồm chỗ ở miễn phí, ăn uống và tài liệu hội nghị. Tổng giải thưởng hơn 10.000 CHF nhằm duy trì đổi mới, cùng môi trường hợp tác tại Innovation Centre Davos để thúc đẩy sáng tạo toàn cầu.
Các dự án đoạt giải
Giải thưởng được trao theo một hạng mục, ghi nhận sáng tạo kỹ thuật và khả năng triển khai hiệu quả.
Giải Nhất (5.000 CHF)
Inspecting Avalanches – Dự án tập trung phát hiện và phân loại lở tuyết bằng kỹ thuật phân tích nâng cao, nâng cao an toàn và quy trình phản ứng.
Giải Nhì (1.500 CHF)
Team Strike – Phát triển chatbot chuyển đổi truy vấn ngôn ngữ tự nhiên thành SQL queries và XML files, tối ưu tương tác cơ sở dữ liệu.
Giải Ba (1.000 CHF)
Sigma – Hệ thống humanoid tương tác với môi trường bằng AI model hiệu quả, đảm bảo data sovereignty (chủ quyền dữ liệu).
Giải Lựa chọn của Hacker
Xem danh sách dự án tại DoraHacks.
Về Nhà tổ chức
Data Migration International
Data Migration International cung cấp giải pháp chuyên sâu về di chuyển dữ liệu (data migration), ứng dụng công nghệ tiên tiến để hỗ trợ tổ chức quản lý chuyển đổi dữ liệu phức tạp. Với chuyên môn kỹ thuật, công ty đã triển khai thành công nhiều dự án quy mô lớn đa ngành, khẳng định năng lực xử lý dữ liệu. Sự tham gia vào lĩnh vực công nghệ và blockchain thể hiện cam kết đổi mới và hiệu quả. Data Migration International hướng đến cung cấp giải pháp mạnh mẽ, đơn giản hóa quy trình quản lý dữ liệu, duy trì vị thế là đối tác đáng tin cậy trong hành trình chuyển đổi số.
-
 @ 4cebd4f5:0ac3ed15
2025-04-16 11:02:45
@ 4cebd4f5:0ac3ed15
2025-04-16 11:02:45Hack The Grid — Level 2 là giai đoạn thứ hai trong chương trình xây dựng bốn cấp độ do LUKSO khởi xướng, tập trung phát triển các ứng dụng phi tập trung nhỏ (mini dApps). Giai đoạn này thu hút 70 hacker đăng ký tham gia, với 41 BUIDLs được phê duyệt. Sự kiện khuyến khích người tham gia đổi mới trong các lĩnh vực như AI agents (trí tuệ nhân tạo), Social DeFi (tài chính phi tập trung xã hội), creator monetization (kiếm tiền cho nhà sáng tạo) và gamification (ứng dụng yếu tố trò chơi). Mục tiêu của hackathon là biến Universal Profiles thành không gian đa năng, tích hợp danh tính số, tương tác xã hội và sáng tạo.
Diễn ra từ tháng 2 đến tháng 4/2025, sự kiện có tổng quỹ tài trợ 150.000 USD bằng đồng LYX, phân bổ qua các cấp độ. Người tham gia có thể tham gia từ xa ở nhiều giai đoạn, với các dự án thành công từ Level 1 đến Level 3 đủ điều kiện nhận hỗ trợ bổ sung tại Vòng tài trợ cộng đồng (Community Grants Round) của Level 4.
Lịch trình hackathon bao gồm các buổi tư vấn (office hours) và chia sẻ kinh nghiệm từ những đội thắng giải trước đó. Bên cạnh thử nghiệm công nghệ, sự kiện thúc đẩy môi trường phát triển hợp tác, chứng minh tiềm năng xây dựng ứng dụng phi tập trung và nuôi dưỡng đổi mới trong hệ sinh thái. Hack The Grid ghi nhận sự tham gia đáng kể cùng những đóng góp dự án nổi bật từ cộng đồng nhà phát triển.
Các dự án đoạt giải
Giải thưởng ORIGIN GRANTS
Hai dự án ở Level 2 được trao Origin Grants nhờ sáng tạo kỹ thuật và định hướng phù hợp với mục tiêu hệ sinh thái.
Hiraeth Mini App: Ứng dụng biến giao dịch blockchain thành các hiện vật số dạng NFT, lưu giữ câu chuyện lịch sử xuyên chuỗi thông qua hình thức thể hiện độc đáo.
Multisend - Defolio: MultiSend cung cấp phương pháp tối ưu để thực hiện nhiều lệnh chuyển token và NFT trên blockchain LUKSO trong một giao dịch duy nhất, nâng cao hiệu quả quản lý tài sản.
Các dự án chiến thắng được đánh giá cao nhờ tập trung vào bảo mật hợp đồng thông minh (smart contract), giao diện thân thiện, kỹ thuật triển khai và giá trị mang lại cho cộng đồng LUKSO. Mỗi đội đoạt Origin Grants nhận 2.250 USD bằng LYX, với 70% được chi trả ngay và phần còn lại phụ thuộc vào việc đạt các KPI tập trung vào mức độ ứng dụng. Những đội thắng cuộc cũng có cơ hội tiến vào Level 4 - Vòng tài trợ cộng đồng - nơi phân bổ thêm 24.000 USD bằng LYX thông qua cơ chế tài trợ bậc hai (quadratic funding).
Xem danh sách đầy đủ các dự án tại DoraHacks.
Về Nhà tổ chức
LUKSO
LUKSO là tổ chức công nghệ chuyên về giải pháp blockchain, tập trung vào lĩnh vực lifestyle số (digital lifestyle) và nền kinh tế sáng tạo (creative economies). Tổ chức này đóng vai trò quan trọng trong việc phát triển các ứng dụng nâng cao danh tính định hướng người dùng (user-centric identity) và quyền sở hữu số. LUKSO là đơn vị tiên phong tạo ra Universal Profiles - hồ sơ phổ quát giúp tương tác liền mạch trên các nền tảng số. Hiện tại, LUKSO hướng đến mở rộng vai trò của blockchain trong trải nghiệm số hàng ngày, ưu tiên bảo mật và khả năng tiếp cận cho đa dạng người dùng trong hệ sinh thái công nghệ.
-
 @ 407556f7:44cf9f3e
2025-04-16 09:42:20
@ 407556f7:44cf9f3e
2025-04-16 09:42:20Em um cenário onde a tecnologia dita o ritmo das transformações sociais e culturais, plataformas de entretenimento como AA123 surgem como protagonistas de uma nova era. Mais do que uma central de jogos, AA123 representa um exemplo concreto de como inovação, experiência do usuário e tecnologia de ponta podem se unir para oferecer algo totalmente fora do comum.
Tecnologia além do básico
O primeiro aspecto que chama a atenção em AA123 é o uso de tecnologia de última geração para garantir uma experiência fluida e atrativa. A plataforma utiliza algoritmos inteligentes que ajustam automaticamente o desempenho gráfico de acordo com o dispositivo do usuário, garantindo jogabilidade de qualidade tanto em smartphones mais simples quanto em computadores de alto desempenho.
Outro ponto notável é a arquitetura responsiva do sistema. Os jogos carregam com rapidez, sem travamentos ou falhas, o que permite que o usuário se concentre no que realmente importa: jogar. Aa123 também investe em atualizações constantes, o que significa melhorias contínuas nos recursos da plataforma, correções de bugs e novos jogos adicionados semanalmente.
Exploração sem limites
Ao entrar na AA123, o jogador mergulha em um mundo diversificado, que mistura lógica, criatividade e emoção. Os jogos disponíveis na plataforma vão desde enigmas mentais e desafios de memória até aventuras visuais com histórias imersivas e trilhas sonoras cinematográficas.
AA123 não se limita a oferecer títulos prontos: muitos de seus jogos têm mecânicas dinâmicas, que se adaptam às escolhas do jogador, tornando cada experiência única. Esse tipo de interatividade favorece o envolvimento emocional e intelectual do usuário, fazendo com que ele volte não apenas pelo jogo, mas pela história que está construindo dentro dele.
A experiência personalizada do jogador
AA123 entende que cada jogador é único, e por isso oferece um sistema de personalização avançado. É possível ajustar configurações de som, gráficos, idioma e até o layout dos controles, garantindo o máximo de conforto durante as sessões de jogo.
Além disso, os perfis dos usuários incluem conquistas desbloqueadas, histórico de atividades e progresso em determinados jogos. Essa sensação de evolução é um estímulo constante, criando um vínculo duradouro entre jogador e plataforma.
Conclusão
AA123 vai além da diversão. Ela representa a fusão entre entretenimento inteligente, design responsivo e experiências personalizadas. Para quem busca uma plataforma atual, tecnológica e com propostas envolventes, AA123 é a escolha ideal. Um espaço onde a inovação não é apenas um diferencial — é parte do DNA.
-
 @ bf95e1a4:ebdcc848
2025-04-16 12:11:27
@ bf95e1a4:ebdcc848
2025-04-16 12:11:27This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our Geyser page!
Proof of Work
Zoom out of time for a while and imagine how the antlers of a magnificent moose buck evolved into being. The main purpose of big antlers in nature is believed to be a way for the buck to impress potential mates. They’re somewhat akin to the feathers of a peacock, or the shroud of any male bird for that matter. The animal is trying to signal that it can thrive in its environment despite its enormous appendage. It’s there to tell the potential mate that this specific specimen will bring her strong, healthy offspring. These are all evolutionary metaphors, of course — the animal itself is probably unaware of signaling anything. For such antlers to evolve into being, a whole lot of moose will have to die early, or at least not get a chance to reproduce, over thousands of generations. In other words, a lot of resources need to be wasted. All of this for the animal to prove its value to potential spouses. Therefore, from the surviving moose's point of view, the aforementioned resources were sacrificed rather than wasted.
The Proof of Work algorithm in Bitcoin does a similar thing. It enables miners to sacrifice a lot of electricity, a real-world resource, to find a certain number, thereby proving that they had to commit a lot of time and effort to do this. Time, by the way, is the scarcest of all resources. Because of all this, a Bitcoin miner is very reluctant to sell Bitcoin at a net loss. The electricity has already been used when the Bitcoin pops into existence, and the miner has no other means of getting his money back than by selling the Bitcoin for more than the cost of the electricity it took to produce them. This is assuming that the mining rig itself has already been paid for. Proof of Work is a way of converting computing power into money, in a sense. Yes, these rigs consume a lot of energy, but the energy consumed correlates directly to the actual value of the created token. Any decrease in the energy expenditure would also lead to a decrease in the value of the token. Not necessarily the price but the actual value. This is the main reason mining algorithms can’t be less resource-consuming or more energy-efficient. “Wasting” energy is the whole point. No “waste,” no proof of commitment.
The fundamental principles of Bitcoin were set in stone in 2008, and block #0, the so-called genesis block, was mined in January 2009. In Bitcoin, a block of transactions is created every ten minutes. In its first four years of existence, these blocks included a 50 Bitcoin block reward given to the miner who found the block. Every four years, this reward is halved so that the maximum amount of Bitcoin that can ever be claimed can never exceed just short of 21 million. Every 2016th block, or roughly every two weeks, the difficulty of finding a new block is re-calibrated so that a block will be found every ten minutes on average. The value of this feature and the impact it has on coin issuance is often understated. It is one of the features of Bitcoin that separates it from gold and other assets in one of the most subtle yet most powerful ways. When the price of gold or silver or oil or any other asset goes up, producing that asset becomes more profitable, and more resources are allocated to produce more of it faster. This, in turn, evens out the price as the total supply of said asset increases.
Gold has been able to maintain or increase its value long term over time because of its high stock-to-flow ratio. Stock refers to the supply of an asset currently available on the market. Flow refers to the amount added to the stock per time unit. The bigger the stock in relation to the flow, the less of an impact on the total supply an increase in the price of a specific asset has. In Bitcoin, a price increase has virtually no impact at all on the coin issuance rate (the flow) since the difficulty of finding the next block in the chain is constantly being optimized for a strict issuance schedule. No other asset has ever behaved like this and we are yet to find out what impact its existence will have on the world economy.
So, how does one mine a block in the Bitcoin blockchain? In short, the mining process goes something like this: every active node in the Bitcoin network stores a copy of the mempool, which contains all Bitcoin transactions that haven’t been confirmed yet. The miner puts as many transactions as the block size allows into the block, usually selecting those with the highest fee first. He then adds a random number, called a nonce, and produces a hash of the entire thing using the SHA-256 hashing algorithm. A hashing algorithm turns data into a string of numbers. If the resulting hash begins with a specific number of zeros decided by the current difficulty of the network, the miner wins the block reward, collects all the fees, and gets to put the block on the blockchain.
The beauty of the system is that it is trivial for the nodes in the network to verify the block so that no double spending can occur, but it’s near impossible to forge a fake hash since the probability of finding one that begins with as many zeros as the difficulty of the Bitcoin network demands is extremely low. To a layman's eye, a hash beginning with a bunch of zeros just looks like a random number, but a person who understands the mathematics behind it sees a different thing. The zeros act as proof of an enormous commitment to trying out different nonces and trying to find a perfect match. If you’re able to understand these huge numbers, you quickly realize that this number must have been created by devoting computing power to doing just that on an absolutely massive scale. The proof is in those zeros.
If you compare just the hash rate of the top five so-called cryptocurrencies, it is obvious that Bitcoin is on a different level security-wise. From a hash rate to security perspective, the Ethereum blockchain is about five times as ineffective, and the Litecoin blockchain about ten times as ineffective as the Bitcoin blockchain at the time of writing.1 This in addition to the obviously more centralized nature of these “alternatives”.
Some of the futurists and doomsday prophets mentioned in chapter four as the people most likely to warn us about the dangers of the impending Artificial Intelligence singularity, believe that we already live in a simulated reality. The main argument for this worldview is that since simulations and computer graphics seem to be getting better at an ever-accelerating rate, we can’t really know if we already live in a simulation or not. To put it another way, we simply have no way of knowing if we live in The Matrix or if our perceived reality is all there is. A really mind-blowing counterargument to this theory is that Bitcoin’s Proof of Work algorithm would eventually slow down the simulation since Proof of Work is verifiable and can’t be simulated itself. Computing power would have to be sacrificed by some entity somewhere, regardless. One question remains, though: can the inhabitants of a simulated reality actually feel or measure a slowdown of the very simulation they live in?
Footnotes:
1. Source: howmanyconfs.com
About the Bitcoin Infinity Academy
The Bitcoin Infinity Academy is an educational project built around Knut Svanholm’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a video in which Knut and Luke de Wolf discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our Geyser page. Signed books, monthly calls, and lots of other benefits are also available.
-
 @ 407556f7:44cf9f3e
2025-04-16 09:41:42
@ 407556f7:44cf9f3e
2025-04-16 09:41:42R8BET é uma plataforma de jogos online inovadora, projetada para trazer entretenimento digital de alta qualidade para jogadores de todas as partes do mundo. Com a crescente popularidade de jogos digitais, a R8BET se destaca pela sua vasta oferta de opções, um design fácil de navegar e um compromisso com a segurança e o bem-estar de seus usuários. Ao longo deste artigo, vamos explorar a introdução à plataforma, seus jogos e a experiência geral do jogador.
Introdução à Plataforma R8BET A R8BET foi desenvolvida para ser uma solução completa para quem busca diversão e emoção no mundo dos jogos online. A plataforma é intuitiva, moderna e oferece uma interface amigável que permite aos jogadores acessarem rapidamente seus jogos favoritos, encontrar novas opções e aproveitar ao máximo sua experiência digital. A plataforma é acessível tanto para iniciantes quanto para jogadores experientes, tornando a navegação simples e eficiente.
Um dos maiores diferenciais da R8bet é sua segurança. A plataforma utiliza as tecnologias mais avançadas de criptografia para proteger os dados pessoais e as transações financeiras dos jogadores, garantindo que todos se sintam seguros e confiantes ao fazer depósitos, retiradas e interagir com a plataforma. Além disso, a equipe de suporte da R8BET está disponível a qualquer hora do dia para esclarecer dúvidas e resolver problemas de forma rápida e eficaz.
Variedade de Jogos na R8BET Na R8BET, a diversão está garantida graças à variedade de jogos disponíveis. A plataforma oferece uma gama diversificada de opções, atendendo aos gostos de todos os tipos de jogadores. Para os que procuram ação e emoção, há uma ampla seleção de jogos rápidos e dinâmicos. Para aqueles que preferem jogos mais estratégicos e desafiadores, a plataforma também oferece várias opções que envolvem habilidade e raciocínio lógico.
Dentre os jogos mais populares, destacam-se as opções de jogos de mesa e apostas esportivas. As apostas esportivas permitem que os jogadores façam suas previsões e ganhem com base nos resultados de eventos esportivos ao redor do mundo, o que adiciona um nível extra de emoção. Para quem gosta de testar a sorte e a habilidade, há também uma grande variedade de jogos de cartas, como pôquer e blackjack.
A R8BET se orgulha de trabalhar com desenvolvedores renomados, oferecendo jogos com gráficos de última geração e jogabilidade fluida. A plataforma constantemente atualiza sua biblioteca de jogos, trazendo novas opções e melhorando a experiência do usuário a cada atualização.
Experiência do Jogador na R8BET A experiência do jogador é o centro de todas as operações da R8BET. Desde o momento em que o usuário acessa a plataforma, ele se depara com um layout bem projetado e fácil de usar. As funcionalidades são claras e diretas, permitindo que os jogadores acessem rapidamente suas opções favoritas. A plataforma também é otimizada para dispositivos móveis, garantindo que a diversão esteja ao alcance de todos, independentemente do lugar.
Outro aspecto fundamental da experiência do jogador é o suporte contínuo. A R8BET oferece um atendimento ao cliente de alta qualidade, disponível a qualquer hora do dia para ajudar com quaisquer dúvidas ou problemas que possam surgir. Isso garante que os jogadores nunca se sintam sozinhos ou desamparados enquanto desfrutam de sua jornada digital.
A plataforma também oferece várias promoções e bônus para jogadores novos e fiéis. Esses incentivos ajudam a manter o interesse dos usuários e recompensam os jogadores por sua lealdade.
Conclusão A R8BET é uma plataforma que tem como foco a qualidade, segurança e a experiência do jogador. Com sua interface intuitiva, ampla variedade de jogos e excelente suporte, é um lugar ideal para quem busca diversão e emoção no universo digital. A R8BET realmente se destaca no mundo dos jogos online, oferecendo uma experiência imersiva e inesquecível para todos.
-
 @ 407556f7:44cf9f3e
2025-04-16 09:40:19
@ 407556f7:44cf9f3e
2025-04-16 09:40:19A tecnologia transformou o modo como nos divertimos, e o 337Bet é um reflexo dessa evolução. Esta plataforma brasileira oferece um ambiente completo de jogos e apostas, ideal para quem busca entretenimento, emoção e desafios. Mais do que apenas um portal, o 337Bet é uma experiência interativa e envolvente, pensada para o público que valoriza usabilidade, segurança e variedade.
Desde o primeiro acesso, fica evidente que a interface do 337Bet foi pensada com atenção aos detalhes. A navegação é simples, as seções são bem organizadas e os recursos são de fácil localização. Essa praticidade torna a plataforma acessível mesmo para quem está começando no mundo das apostas online.
Diversão em múltiplas formas
O grande atrativo do 337bet está em sua diversidade. A plataforma não limita a experiência a um único tipo de jogo. Pelo contrário, ela abre um leque de possibilidades para todos os estilos. As apostas esportivas são o carro-chefe, oferecendo cobertura de campeonatos nacionais e internacionais. Futebol, basquete, tênis, MMA e até esportes eletrônicos estão entre as opções disponíveis, com cotações atualizadas em tempo real.
Outro destaque são os jogos de habilidade e sorte. Com gráficos de alta definição e mecânicas modernas, os jogadores podem se envolver em partidas que exigem estratégia, raciocínio lógico e decisões rápidas. Isso garante uma experiência dinâmica e imprevisível — exatamente o que muitos procuram em momentos de lazer.
O 337Bet também oferece jogos com rodadas bônus e premiações acumuladas, tornando a diversão ainda mais interessante. Com isso, o jogador tem múltiplas formas de se envolver, seja apostando em um evento esportivo ou testando a sorte em rodadas emocionantes.
A experiência do usuário em primeiro lugar
A plataforma preza por uma experiência fluida e segura. Todos os dados do usuário são protegidos por criptografia avançada, o que proporciona tranquilidade e confiança durante o uso. O sistema de pagamento é eficiente e suporta os principais métodos disponíveis no Brasil, incluindo Pix, transferência bancária e carteiras digitais.
Outro ponto importante é o suporte técnico. O atendimento funciona 24 horas por dia e é realizado por uma equipe preparada para resolver qualquer tipo de demanda. A comunicação é rápida e eficaz, o que reforça a imagem de responsabilidade da plataforma.
Além disso, o 337Bet investe em bonificações e promoções para novos usuários e jogadores frequentes. Essas ações mantêm os usuários engajados e ampliam as chances de sucesso, sem abrir mão da diversão.
Conclusão
O 337Bet é uma escolha certeira para quem deseja unir entretenimento com oportunidades reais de ganho. Com uma interface moderna, jogos variados e suporte dedicado, a plataforma proporciona uma experiência completa para quem busca emoção e diversão com segurança. Se você ainda não conhece, vale a pena explorar tudo que o 337Bet tem a oferecer.
-
 @ fd06f542:8d6d54cd
2025-04-16 09:36:18
@ fd06f542:8d6d54cd
2025-04-16 09:36:18NIP-17
Private Direct Messages
draftoptionalThis NIP defines an encrypted direct messaging scheme using NIP-44 encryption and NIP-59 seals and gift wraps.
Direct Message Kind
Kind
14is a chat message.ptags identify one or more receivers of the message.jsonc { "id": "<usual hash>", "pubkey": "<sender-pubkey>", "created_at": "<current-time>", "kind": 14, "tags": [ ["p", "<receiver-1-pubkey>", "<relay-url>"], ["p", "<receiver-2-pubkey>", "<relay-url>"], ["e", "<kind-14-id>", "<relay-url>"] // if this is a reply ["subject", "<conversation-title>"], // rest of tags... ], "content": "<message-in-plain-text>", }.contentMUST be plain text. Fieldsidandcreated_atare required.An
etag denotes the direct parent message this post is replying to.qtags MAY be used when citing events in the.contentwith NIP-21.json ["q", "<event-id> or <event-address>", "<relay-url>", "<pubkey-if-a-regular-event>"]Kind
14s MUST never be signed. If it is signed, the message might leak to relays and become fully public.File Message Kind
jsonc { "id": "<usual hash>", "pubkey": "<sender-pubkey>", "created_at": "<current-time>", "kind": 15, "tags": [ ["p", "<receiver-1-pubkey>", "<relay-url>"], ["p", "<receiver-2-pubkey>", "<relay-url>"], ["e", "<kind-14-id>", "<relay-url>", "reply"], // if this is a reply ["subject", "<conversation-title>"], ["file-type", "<file-mime-type>"], ["encryption-algorithm", "<encryption-algorithm>"], ["decryption-key", "<decryption-key>"], ["decryption-nonce", "<decryption-nonce>"], ["x", "<the SHA-256 hexencoded string of the file>"], // rest of tags... ], "content": "<file-url>" }Kind 15 is used for sending encrypted file event messages:
file-type: Specifies the MIME type of the attached file (e.g.,image/jpeg,audio/mpeg, etc.).encryption-algorithm: Indicates the encryption algorithm used for encrypting the file. Supported algorithms may includeaes-gcm,chacha20-poly1305,aes-cbcetc.decryption-key: The decryption key that will be used by the recipient to decrypt the file.decryption-nonce: The decryption nonce that will be used by the recipient to decrypt the file.content: The URL of the file (<file-url>).xcontaining the SHA-256 hexencoded string of the file.size(optional) size of file in bytesdim(optional) size of the file in pixels in the form<width>x<height>blurhash(optional) the blurhash to show while the client is loading the filethumb(optional) URL of thumbnail with same aspect ratio (encrypted with the same key, nonce)fallback(optional) zero or more fallback file sources in caseurlfails
Just like kind 14, kind
15s MUST never be signed.Chat Rooms
The set of
pubkey+ptags defines a chat room. If a newptag is added or a current one is removed, a new room is created with a clean message history.Clients SHOULD render messages of the same room in a continuous thread.
An optional
subjecttag defines the current name/topic of the conversation. Any member can change the topic by simply submitting a newsubjectto an existingpubkey+p-tags room. There is no need to sendsubjectin every message. The newestsubjectin the thread is the subject of the conversation.Encrypting
Following NIP-59, the unsigned
kind:14&kind:15chat messages must be sealed (kind:13) and then gift-wrapped (kind:1059) to each receiver and the sender individually.jsonc { "id": "<usual hash>", "pubkey": randomPublicKey, "created_at": randomTimeUpTo2DaysInThePast(), "kind": 1059, // gift wrap "tags": [ ["p", receiverPublicKey, "<relay-url>"] // receiver ], "content": nip44Encrypt( { "id": "<usual hash>", "pubkey": senderPublicKey, "created_at": randomTimeUpTo2DaysInThePast(), "kind": 13, // seal "tags": [], // no tags "content": nip44Encrypt(unsignedKind14, senderPrivateKey, receiverPublicKey), "sig": "<signed by senderPrivateKey>" }, randomPrivateKey, receiverPublicKey ), "sig": "<signed by randomPrivateKey>" }The encryption algorithm MUST use the latest version of NIP-44.
Clients MUST verify if pubkey of the
kind:13is the same pubkey on thekind:14, otherwise any sender can impersonate others by simply changing the pubkey onkind:14.Clients SHOULD randomize
created_atin up to two days in the past in both the seal and the gift wrap to make sure grouping bycreated_atdoesn't reveal any metadata.The gift wrap's
p-tag can be the receiver's main pubkey or an alias key created to receive DMs without exposing the receiver's identity.Clients CAN offer disappearing messages by setting an
expirationtag in the gift wrap of each receiver or by not generating a gift wrap to the sender's public keyPublishing
Kind
10050indicates the user's preferred relays to receive DMs. The event MUST include a list ofrelaytags with relay URIs.jsonc { "kind": 10050, "tags": [ ["relay", "wss://inbox.nostr.wine"], ["relay", "wss://myrelay.nostr1.com"], ], "content": "", // other fields... }Clients SHOULD publish kind
14events to the10050-listed relays. If that is not found that indicates the user is not ready to receive messages under this NIP and clients shouldn't try.Relays
It's advisable that relays do not serve
kind:1059to clients other than the ones tagged in them.It's advisable that users choose relays that conform to these practices.
Clients SHOULD guide users to keep
kind:10050lists small (1-3 relays) and SHOULD spread it to as many relays as viable.Benefits & Limitations
This NIP offers the following privacy and security features:
- No Metadata Leak: Participant identities, each message's real date and time, event kinds, and other event tags are all hidden from the public. Senders and receivers cannot be linked with public information alone.
- No Public Group Identifiers: There is no public central queue, channel or otherwise converging identifier to correlate or count all messages in the same group.
- No Moderation: There are no group admins: no invitations or bans.
- No Shared Secrets: No secret must be known to all members that can leak or be mistakenly shared
- Fully Recoverable: Messages can be fully recoverable by any client with the user's private key
- Optional Forward Secrecy: Users and clients can opt-in for "disappearing messages".
- Uses Public Relays: Messages can flow through public relays without loss of privacy. Private relays can increase privacy further, but they are not required.
- Cold Storage: Users can unilaterally opt-in to sharing their messages with a separate key that is exclusive for DM backup and recovery.
The main limitation of this approach is having to send a separate encrypted event to each receiver. Group chats with more than 100 participants should find a more suitable messaging scheme.
Implementation
Clients implementing this NIP should by default only connect to the set of relays found in their
kind:10050list. From that they should be able to load all messages both sent and received as well as get new live updates, making it for a very simple and lightweight implementation that should be fast.When sending a message to anyone, clients must then connect to the relays in the receiver's
kind:10050and send the events there but can disconnect right after unless more messages are expected to be sent (e.g. the chat tab is still selected). Clients should also send a copy of their outgoing messages to their ownkind:10050relay set.Examples
This example sends the message
Hola, que tal?fromnsec1w8udu59ydjvedgs3yv5qccshcj8k05fh3l60k9x57asjrqdpa00qkmr89mtonsec12ywtkplvyq5t6twdqwwygavp5lm4fhuang89c943nf2z92eez43szvn4dt.The two final GiftWraps, one to the receiver and the other to the sender, respectively, are:
json { "id":"2886780f7349afc1344047524540ee716f7bdc1b64191699855662330bf235d8", "pubkey":"8f8a7ec43b77d25799281207e1a47f7a654755055788f7482653f9c9661c6d51", "created_at":1703128320, "kind":1059, "tags":[ [ "p", "918e2da906df4ccd12c8ac672d8335add131a4cf9d27ce42b3bb3625755f0788"] ], "content":"AsqzdlMsG304G8h08bE67dhAR1gFTzTckUUyuvndZ8LrGCvwI4pgC3d6hyAK0Wo9gtkLqSr2rT2RyHlE5wRqbCOlQ8WvJEKwqwIJwT5PO3l2RxvGCHDbd1b1o40ZgIVwwLCfOWJ86I5upXe8K5AgpxYTOM1BD+SbgI5jOMA8tgpRoitJedVSvBZsmwAxXM7o7sbOON4MXHzOqOZpALpS2zgBDXSAaYAsTdEM4qqFeik+zTk3+L6NYuftGidqVluicwSGS2viYWr5OiJ1zrj1ERhYSGLpQnPKrqDaDi7R1KrHGFGyLgkJveY/45y0rv9aVIw9IWF11u53cf2CP7akACel2WvZdl1htEwFu/v9cFXD06fNVZjfx3OssKM/uHPE9XvZttQboAvP5UoK6lv9o3d+0GM4/3zP+yO3C0NExz1ZgFmbGFz703YJzM+zpKCOXaZyzPjADXp8qBBeVc5lmJqiCL4solZpxA1865yPigPAZcc9acSUlg23J1dptFK4n3Tl5HfSHP+oZ/QS/SHWbVFCtq7ZMQSRxLgEitfglTNz9P1CnpMwmW/Y4Gm5zdkv0JrdUVrn2UO9ARdHlPsW5ARgDmzaxnJypkfoHXNfxGGXWRk0sKLbz/ipnaQP/eFJv/ibNuSfqL6E4BnN/tHJSHYEaTQ/PdrA2i9laG3vJti3kAl5Ih87ct0w/tzYfp4SRPhEF1zzue9G/16eJEMzwmhQ5Ec7jJVcVGa4RltqnuF8unUu3iSRTQ+/MNNUkK6Mk+YuaJJs6Fjw6tRHuWi57SdKKv7GGkr0zlBUU2Dyo1MwpAqzsCcCTeQSv+8qt4wLf4uhU9Br7F/L0ZY9bFgh6iLDCdB+4iABXyZwT7Ufn762195hrSHcU4Okt0Zns9EeiBOFxnmpXEslYkYBpXw70GmymQfJlFOfoEp93QKCMS2DAEVeI51dJV1e+6t3pCSsQN69Vg6jUCsm1TMxSs2VX4BRbq562+VffchvW2BB4gMjsvHVUSRl8i5/ZSDlfzSPXcSGALLHBRzy+gn0oXXJ/447VHYZJDL3Ig8+QW5oFMgnWYhuwI5QSLEyflUrfSz+Pdwn/5eyjybXKJftePBD9Q+8NQ8zulU5sqvsMeIx/bBUx0fmOXsS3vjqCXW5IjkmSUV7q54GewZqTQBlcx+90xh/LSUxXex7UwZwRnifvyCbZ+zwNTHNb12chYeNjMV7kAIr3cGQv8vlOMM8ajyaZ5KVy7HpSXQjz4PGT2/nXbL5jKt8Lx0erGXsSsazkdoYDG3U", "sig":"a3c6ce632b145c0869423c1afaff4a6d764a9b64dedaf15f170b944ead67227518a72e455567ca1c2a0d187832cecbde7ed478395ec4c95dd3e71749ed66c480" }json { "id":"162b0611a1911cfcb30f8a5502792b346e535a45658b3a31ae5c178465509721", "pubkey":"626be2af274b29ea4816ad672ee452b7cf96bbb4836815a55699ae402183f512", "created_at":1702711587, "kind":1059, "tags":[ [ "p", "44900586091b284416a0c001f677f9c49f7639a55c3f1e2ec130a8e1a7998e1b"] ], "content":"AsTClTzr0gzXXji7uye5UB6LYrx3HDjWGdkNaBS6BAX9CpHa+Vvtt5oI2xJrmWLen+Fo2NBOFazvl285Gb3HSM82gVycrzx1HUAaQDUG6HI7XBEGqBhQMUNwNMiN2dnilBMFC3Yc8ehCJT/gkbiNKOpwd2rFibMFRMDKai2mq2lBtPJF18oszKOjA+XlOJV8JRbmcAanTbEK5nA/GnG3eGUiUzhiYBoHomj3vztYYxc0QYHOx0WxiHY8dsC6jPsXC7f6k4P+Hv5ZiyTfzvjkSJOckel1lZuE5SfeZ0nduqTlxREGeBJ8amOykgEIKdH2VZBZB+qtOMc7ez9dz4wffGwBDA7912NFS2dPBr6txHNxBUkDZKFbuD5wijvonZDvfWq43tZspO4NutSokZB99uEiRH8NAUdGTiNb25m9JcDhVfdmABqTg5fIwwTwlem5aXIy8b66lmqqz2LBzJtnJDu36bDwkILph3kmvaKPD8qJXmPQ4yGpxIbYSTCohgt2/I0TKJNmqNvSN+IVoUuC7ZOfUV9lOV8Ri0AMfSr2YsdZ9ofV5o82ClZWlWiSWZwy6ypa7CuT1PEGHzywB4CZ5ucpO60Z7hnBQxHLiAQIO/QhiBp1rmrdQZFN6PUEjFDloykoeHe345Yqy9Ke95HIKUCS9yJurD+nZjjgOxZjoFCsB1hQAwINTIS3FbYOibZnQwv8PXvcSOqVZxC9U0+WuagK7IwxzhGZY3vLRrX01oujiRrevB4xbW7Oxi/Agp7CQGlJXCgmRE8Rhm+Vj2s+wc/4VLNZRHDcwtfejogjrjdi8p6nfUyqoQRRPARzRGUnnCbh+LqhigT6gQf3sVilnydMRScEc0/YYNLWnaw9nbyBa7wFBAiGbJwO40k39wj+xT6HTSbSUgFZzopxroO3f/o4+ubx2+IL3fkev22mEN38+dFmYF3zE+hpE7jVxrJpC3EP9PLoFgFPKCuctMnjXmeHoiGs756N5r1Mm1ffZu4H19MSuALJlxQR7VXE/LzxRXDuaB2u9days/6muP6gbGX1ASxbJd/ou8+viHmSC/ioHzNjItVCPaJjDyc6bv+gs1NPCt0qZ69G+JmgHW/PsMMeL4n5bh74g0fJSHqiI9ewEmOG/8bedSREv2XXtKV39STxPweceIOh0k23s3N6+wvuSUAJE7u1LkDo14cobtZ/MCw/QhimYPd1u5HnEJvRhPxz0nVPz0QqL/YQeOkAYk7uzgeb2yPzJ6DBtnTnGDkglekhVzQBFRJdk740LEj6swkJ", "sig":"c94e74533b482aa8eeeb54ae72a5303e0b21f62909ca43c8ef06b0357412d6f8a92f96e1a205102753777fd25321a58fba3fb384eee114bd53ce6c06a1c22bab" } -
 @ fd06f542:8d6d54cd
2025-04-16 09:35:45
@ fd06f542:8d6d54cd
2025-04-16 09:35:45- 第三章、NIP-03: OpenTimestamps Attestations for Events
- 第四章、NIP-04: Encrypted Direct Message
- 第五章、NIP-05: Mapping Nostr keys to DNS-based internet identifiers
- 第六章、NIP-06: Basic key derivation from mnemonic seed phrase
- 第七章、NIP-07: window.nostr capability for web browsers
- 第八章、NIP-08: Handling Mentions --- unrecommended: deprecated in favor of NIP-27
- 第九章、NIP-09: Event Deletion Request
- 第十章、NIP-10: Text Notes and Threads
- 第十一章、NIP-11: Relay Information Document
- 第十二章、NIP-13: Proof of Work
- 第十三章、NIP-14: Subject tag in text events
- 第十四章、NIP-15: Nostr Marketplace (for resilient marketplaces)
- 第十五章、NIP-17: Private Direct Messages
-
 @ 5188521b:008eb518
2025-04-16 09:09:48
@ 5188521b:008eb518
2025-04-16 09:09:48Why write a book about time?
My obsession with time actually started when I read An Occurrence at Owl Creek Bridge (written by Ambrose Bierce in 1890).
We can’t play around with time in the real world, but in fiction, anything goes. The story of Owl Creek Bridge follows a Confederate sympathiser condemned to death by hanging. In its three sections, time goes forward and back, speeds up and slows down, and at one point stops entirely. Every time I read it, I feel like I’m physically travelling in time.
I went a bit deeper into the topic back in 2020. Due to the lockdown, I had a lot of time on my hands to do some research. Like many of my stories, this one started with a question: I started to ask ‘what actually is time’?
What did you find out?
I found out that time is a rabbit hole! Nobody knows exactly what it is. We know that it’s conceptual, personal, and malleable, however accurate our watches are. Some philosophers and scientists (Jose Luis Borges and Carlo Rovelli) claim it doesn’t exist.
I guess what I discovered is that we all need time to survive. It’s how we process our experience here on Earth.
Who are the characters in this book?
The book tells the story of Luca Cangemi, an Italian philosophy professor giving a lecture on the subject of time. The chapters follow the possible lives of other characters in the lecture hall. Then, Cangemi makes an astounding discovery. It’s something that allows him to change the fabric of time for everyone (including the readers).
Why use 15 characters to present the story?
I like to challenge readers, so I made the story a bit of a puzzle. In fact, there is something called a 15 puzzle — it’s a block of 15 pictured tiles and one space. You have to slide them to arrange the correctly ordered image. There’s more about the puzzle in the book.
What about the Timechain? Is there any link there?
Not exactly. The book doesn’t mention it, but isn’t everything an analogy for bitcoin? Soon after finishing this book, I got orange pilled and began to read more and more about bitcoin, including Gigi’s fantastic essay Bitcoin is Time.
Time is all we have though. Even though it might be hard to understand, we have to try.
Who do you think would enjoy this book?
I’d say sci-fi fans. Those who aren’t afraid to be challenged. One cool thing about the bitcoin community is that they are dialled in to technical stuff and they are avid readers. Why not give fiction a try too? Sometimes we learn more from getting the answer ourselves through stories.
What are you working on next?
I have three other writing projects on the go, so there is no time to rest. Very soon, I’ll be publishing a children’s book about horrible uncles. I’m editing the next installment of 21 Futures too. Financial Fallout will be out in early 2025. And finally, I’m writing content and newsletters for bitcoin founders and companies. If I’m not trying to sell you a book, I’ll be doing my best to orange-pill you, ha ha.
Thanks for talking with us, Philip, and good look with all those writing projects.
Order the book in our store.
Here’s a passage from Fifteen Shades of Time.
The Direction of Everything
Luca Cangemi and everyone he knows will be long dead, but the moment will come. Theoretical physicists believe it will be anywhere from 2.8 to 22 billion years in the future. In that moment, everything reverses.
The Big Crunch is a cosmological event in our future and our past in which the density of matter grows sufficiently that gravitational attraction overcomes the expansion that began with the Big Bang. Entropy reverses and the second law is broken. Chaos retreats.
Order is regained as space contracts. Broken rocks reform and decayed bodies reanimate. We live our lives in reverse, unexperiencing everything we did the first time around, moving backwards, shrinking towards birth. Instead of questions about creation, we search for the harbinger of order. Who began this? What is our final form?
Luca imagines the crowds at his book signings dissipating and the offices of his academic fellowships decreasing in size. Wrong turns are righted and his family grows closer. His briefcase heals itself and he returns it to his mother. Life rewinds back to him as a young boy, unreading the words that inspired him to look for meaning in all of this. If it can all be reversed, are all shared experiences undone? All bonds broken? Luca returns into his parents, then ancestors, apes, microbes, and nothing. The earth, the planets and stars all merge into one perfectly ordered mass.
Yet, this is not an end, but another beginning in which the universe is reborn in another bang. Galaxies, planets, plants, and philosophy professors will live the same lives as they did billions of years before (and after). The process of positive and negative entropy repeats and we all make the same mistakes again.
Time elapsed: the infinitely repeating cycle of a universe
Philip Charter is a totally human writer, laser-focused on spreading the gospel of bitcoin and cypherpunk ideals. He is the editor of the 21 Futures anthology series and has published four books of short fiction. After leaving the UK to search for more sun, he now resides in Gran Canaria, Spain.
-
 @ 7d33ba57:1b82db35
2025-04-16 08:31:09
@ 7d33ba57:1b82db35
2025-04-16 08:31:09Iceland is a surreal blend of volcanic power, glacial beauty, and rugged wilderness. From black sand beaches and steaming geothermal pools to massive waterfalls and the magical northern lights, it’s a dream destination for nature lovers and road trippers.
Whether you want to soak in a hot spring, chase waterfalls, hike volcanoes, or just drive through epic landscapes that look straight out of a fantasy film, Iceland has it all.
🧭 Top Things to Do in Iceland
1️⃣ The Golden Circle
The perfect intro loop from Reykjavik: - Þingvellir National Park – Rift valley between tectonic plates + historic parliament site
- Gullfoss – Thundering two-tier waterfall
- Geysir geothermal area – Home of the original geyser (and Strokkur, which erupts every few minutes)2️⃣ South Coast Highlights
- Seljalandsfoss & Skógafoss – Iconic waterfalls you can walk behind or get soaked by
- Reynisfjara Black Sand Beach – With eerie basalt columns and crashing Atlantic waves
- Sólheimajökull Glacier – Guided glacier walks or ice climbs
- Vík – Quaint village with epic coastal views
3️⃣ Snæfellsnes Peninsula
- Often called “Iceland in Miniature”
- Includes Kirkjufell mountain, lava fields, fishing villages, and coastal cliffs
- Great alternative if you’re short on time but want variety
4️⃣ The Blue Lagoon (or better: Sky Lagoon)
- Iconic milky-blue geothermal spa near the airport
- Sky Lagoon near Reykjavik is newer, less touristy, and has a 7-step ritual sauna-spa experience with ocean views
5️⃣ Chase the Northern Lights
- Best seen September to April
- Get away from city lights and use apps or tours to track them
- Clear skies, cold nights, and some patience = magic
🚗 Epic Road Trip: The Ring Road
- Iceland’s main highway (Route 1) loops the entire island
- Takes about 7–10 days to do well
- You’ll see glaciers, fjords, waterfalls, volcanoes, and maybe even puffins and reindeer
- Rent a campervan or car and take it slow—it’s all about the journey
🍽️ What to Eat in Iceland
- Lamb stew (kjötsúpa) – Warm and hearty
- Plokkfiskur – Creamy fish and potato comfort food
- Skyr – Icelandic yogurt, smooth and protein-rich
- Hot dogs from Bæjarins Beztu – Iconic street food in Reykjavik
🗓️ When to Go
- Summer (June–Aug): Midnight sun, hiking, puffins, easier driving
- Winter (Oct–Mar): Aurora season, ice caves, snowy wonderland
- Shoulder seasons: Fewer crowds, lower prices, unpredictable weather (pack layers!)
✨ Quick Tips
✅ Tap water = some of the purest in the world
✅ Always check road and weather conditions—they can change fast
✅ Download Veður (weather) and SafeTravel.is for safety updates
✅ Book hot springs, ice cave tours, and northern lights hunts in advance during high season -
 @ da0b9bc3:4e30a4a9
2025-04-16 08:28:24
@ da0b9bc3:4e30a4a9
2025-04-16 08:28:24Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/944844
-
 @ ef53426a:7e988851
2025-04-16 09:34:47
@ ef53426a:7e988851
2025-04-16 09:34:47‘Write what you know’ is good advice… until the market changes.
Then you have to learn something new. You have to make sure your words are still valuable so you avoid writing to an audience of none.
I’ve revamped my writing business at least four times. Sometimes through necessity and other times because of my vision. One thing is for sure: the writing business is not a linear path to success, and sometimes, you have to pivot.
Drastic Changes to My Writing Business
1. From Literary Magazines to Books

I published my first story in Flash Fiction Magazine in 2016. The publications came thick and fast after that. Write, edit, submit, revise, submit and go again. I was prolific — around 30 short stories accepted in under two years. But my goal was not to earn big bucks or become the next Neil Gaiman. I just wanted to share my creativity with readers.
I won a competition, placed in more, and even received payment here and there. But literary magazines are read almost exclusively by writers. The audience is niche.
If you want the wider world to know you are a writer, give them a book. Of course, I quickly realised that few agents or publishers were willing to take a gamble on short fiction, so I collated my already available works and self-published.
The difference was palpable. Friends, acquaintances, and people I’d never even met read my stories and saw me as a writer — a real one.
As long as you publish your best work, books give you a massive injection of confidence. Soon, I was teaching workshops and believed that I could offer much much more.
2. From English Teacher to Writing Coach

If you think the pay for writers sucks, try being an English teacher! I’d been working for predatory academies in a dead-end industry for 8+ years and decided enough was enough.
After helping hundreds of students with writing tasks (and being an author myself), I launched my online business — English Writing Coach.
There are millions of teachers and writers out there, but I noticed that no one was specifically helping multilingual writers to improve the quality of their text and succeed in business. No, I wasn’t a seven-figure copywriter saying ‘Follow my strategy for success’. In fact, I hadn’t done much freelance writing, but I backed myself to guide clients towards their goals.
Running your own business involves a lot of failure and readjustment. A lot. The lows can be crushing. But I love that I control who I work with and what I do. And I get to talk about writing all day!
After several years (and a lot of missteps along the way), I now run group courses and a community with over 100 members.
3. From Professional Coach to Totally Human Ghostwriter

In 2023, AI crashed the party. The effects of rate cuts, shrinking marketing budgets and layoffs are still being felt today.
I do most of my marketing on LinkedIn, and there, I turned the dial from 50 to 100. The dial wasn’t quantity, effort, or the number of topics I wrote about. It was my personality.
After reading so many tired ‘tips and tricks’ (as well as ChatGPT copypastas), I decided to amp up my own writing voice.
I wrote stories about my wins and failures. I made fun of crumby 4 am writing routines and yawn-worthy buzzwords. I wrote slideshows about saving kittens going on a quest with a badger. I raged at industry discrimination. Focusing on my writing persona positioned me as a unique voice, not a follower (or as I once put it, ‘buttocks, not white noise’).
Now I help bitcoin and nostr clients bring out their own writing voice (or that of their employer). I work with a freedom publishing house, a social app, a btc neobank suite, and a backend facilitation and compliance company.
Check my website:
Plus, I write for magazines and outlets, as well as editing bitcoin books and helping with launch campaigns.
4. From Traditional Author to Self-Publishing a Kids’ Book
Alongside my content writing and other projects, I continued writing fiction, publishing two novellas with indie presses in the UK and US. Those experiences were positive but didn’t bring me thousands of sales or many readers outside of my circle.
You might have guessed what comes next, as I’m not someone who stands still. Like the resplendent Optimus Prime, I transformed.

I’ve had a children’s book in the works for a little while, and without an agent or best mate who works for Scholastic, I’m returning to self-publishing. The A-Z of Rotten Uncles will be the third book I’ve self-published (and will perhaps be the most personal, as I am, indeed, a very rotten uncle). The book was published in 2024 and it has since been translated in to Italian and Spanish.
I’m so determined to get this book into the hands of nieces and nephews around the world, that I’m teaming up with an illustrator friend and some translators in my network too.
You’re probably as confused about my writing career trajectory as I am.
There is no clear path, career ladder, silver bullet, well-placed stepping stone, or any other metaphor you care to imagine. Writers make their own way, and they have to adapt.
However, one thing has NOT changed — an unwavering belief that my creativity and writing voice are valuable.
What I offer may change over time, but I will continue to deliver the words which keep my creative spirit and my business running.
-
 @ ffbcb706:b0574044
2025-04-16 08:11:12
@ ffbcb706:b0574044
2025-04-16 08:11:12I like to have openletter on the Nostr protocol
-
 @ 2b24a1fa:17750f64
2025-04-16 07:55:24
@ 2b24a1fa:17750f64
2025-04-16 07:55:24„Ich bin der Weg“, sagt Jesus am Kreuz, in der Mitte. Symbolisch zwischen Übertreibung und Verblendung. Wenn dieser Maßstab an das Gros der Nachrichten angelegt wird, die wir in den letzten fünf Jahren vermittelt bekamen, landen wir selten in der Mitte. Aber nur der gelassene Blick in Richtung Übertreibung und Verblendung, lässt die Mitte zwischen ihnen erspüren.
https://soundcloud.com/radiomuenchen/angst-frisst-seelen-von-j-rgen?
Auf den Weg dorthin begibt sich eine Friedensprozession am Karfreitag, den 18. April ab 13 Uhr, ausgehend vom Postplatz in Dresden. Hören Sie Jürgen Flieges Text: „Angst frisst Seelen“.
Sprecher: Guido de Gyrich.
-
 @ 2b24a1fa:17750f64
2025-04-16 07:52:59
@ 2b24a1fa:17750f64
2025-04-16 07:52:59Am 22. November 1963 starb US-Präsident John F. Kennedy bei einem Attentat in Dallas durch zwei Gewehrschüsse. Als möglicher Täter wurde Lee Harvey Oswald verhaftet und zwei Tage später erschossen. Kennedys Amtsnachfolger Lyndon B. Johnson setzte einen Untersuchungsausschuss ein: die Warren-Kommission, benannt nach deren Leiter Earl Warren, höchster Richter am Supreme Court, dem Obersten Gerichtshof der Vereinigten Staaten. Die Warren-Kommission bestätigte die Einzeltäter-These. Dennoch kursierten und kursieren bis heute zahlreiche Gerüchte und Verschwörungstheorien. Mit dem Totschlag-Argument „Nationale Sicherheit“ verweigerte die CIA die Herausgabe ihrer Ermittlungsakten und nährte gerade dadurch den Verdacht, sie selbst habe Kennedy ermorden lassen. Über 60 Jahre später gibt Präsident Trump nun die Akten frei.
https://soundcloud.com/radiomuenchen/trump-die-jfk-files?
\ Die Meinungen gehen auseinander: Für die einen enthalten die Akten wenig Neues, für die anderen ergeben sich neue Zweifel an der Einzeltäter-These. Unsere Autorin Gaby Weber befasst sich schon seit vielen Jahren mit der Materie, unter anderem in ihrem Buch „CIA, Drogen, Gehirnwäsche“ von 1981. Außerdem recherchiert sie seit langem über illegale Atomwaffentests des Pentagons in Argentinien 1960. Zwischen den illegalen Atomwaffentest und Kennedys Tod könnte es einen Zusammenhang geben, glaubt Gaby Weber und hat einen neuen Antrag auf Aktenfreigabe gestellt. Hören Sie ihren Beitrag: „Trump & die JFK-Files“.
Sprecherin: Gaby Weber
Redaktion: Jonny Rieder
Radio München\ www.radiomuenchen.net/\ @radiomuenchen\ www.facebook.com/radiomuenchen\ www.instagram.com/radio_muenchen/\ twitter.com/RadioMuenchen\ odysee.com/@RadioMuenchen.net:9\ rumble.com/user/RadioMunchen
Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen.
GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS\ Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 0121e6f7:1a7c8df4
2025-04-16 12:37:37
@ 0121e6f7:1a7c8df4
2025-04-16 12:37:37hi2
-
 @ 2b24a1fa:17750f64
2025-04-16 07:40:49
@ 2b24a1fa:17750f64
2025-04-16 07:40:49„Auch wenn das völliger Wahnsinn ist“ … soll der Freie-Wähler-Chef gesagt haben: „Die CSU kann auch ohne uns im Bundesrat zustimmen. Deswegen bringt es nichts, wenn wir uns weiter dagegenstellen.“ Man opfert also die eigene Einstellung und stimmt für das Gegenteil, legitimiert also den Wahnsinn, weil es nichts bringt? Hört mit dieser Schizophrenie auf – möchte man schreien. Denn täglich hören wir von führenden deutschen Politikern, die ohne relevante Begründung die irrwitzigsten Entscheidungen treffen und den Souverän übergehen, als wäre er Luft.
Jetzt sollte dieser Souverän, der Bürger aber nicht mit Hilflosigkeit reagieren, meint Ludwig F. Badenhagen, denn es existiere ein einfacher als auch wirksamer Lösungsansatz. Hören Sie seinen Text: „Wie wir die Kriegstreiber stoppen“. Sprecherin: Sabrina Khalil.
Sie hörten: „Wie wir die Kriegstreiber stoppen“ von Ludwig F. Badenhagen. Ludwig F. Badenhagen ist ein Pseudonym für einen Autor mit deutschen Wurzeln, der das Geschehen in Deutschland und Europa aus seiner Wahlheimat Südafrika beobachtet. Er ist international agierender Manager mit globalem Netzwerk und verfügt dadurch über tiefe Einblicke in Konzerne und Politik. Sein Text erschien zunächst auf Milosz Matuscheks Friedensinitiativseite „Friedenstaube“.
-
 @ 2b24a1fa:17750f64
2025-04-16 07:32:45
@ 2b24a1fa:17750f64
2025-04-16 07:32:45Wo läßt es sich trefflicher plaudern als am Küchentisch. Es muß ja nicht unbedingt der eigene sein. Hauptsache, es sitzen vergnügte Menschen reinen Herzens daran, wie zum Beispiel die Herren Helmut Schleich und Franz Esser.
https://soundcloud.com/radiomuenchen/am-kuchentisch-mit-schleich-und-esser
-
 @ b0137b96:304501dd
2025-04-16 06:33:23
@ b0137b96:304501dd
2025-04-16 06:33:23In recent years, the Telugu film industry has witnessed a remarkable transformation, with a significant surge in the popularity of Hollywood movies in Telugu dubbed. This trend reflects a growing appetite among Telugu audiences for diverse storytelling and international cinematic experiences. While regional films continue to thrive, the increasing demand for Hollywood movies in Telugu dubbed speaks to a cultural shift and a desire for global entertainment. Two films that exemplify this trend are Medusa: Beauty is the Beast and its sequel, Medusa’s Venom. These movies not only showcase the appeal of Hollywood narratives but also demonstrate how familiar mythological themes can be reimagined in a contemporary context, resonating with Telugu viewers.
This article explores these two films and their significance in the broader landscape of Hollywood movies in Telugu dubbed, highlighting how this trend is reshaping the viewing habits and preferences of Telugu cinema enthusiasts.
Hollywood Movies in Telugu Dubbed
Medusa: Beauty is the Beast – Hollywood movie in Telugu dubbed (2021) Medusa: Beauty is the Beast is a horror movie that puts a modern twist on Greek mythology. After being bitten by a lethal snake, a young woman named Carly experiences changes in her senses and appearance as she sheds her old self and slowly turns into a deadly weapon. This Hollywood movie in Telugu dubbed is directed by Jeffrey and Co. and features a powerful performance by Megan Purvis as the lead actress, Carly. Most of the film takes place in a caravan site, which serves as a sanctuary for women under the protection of Medusa.
The Hollywood movie in Telugu dubbed tackles topical issues wrapped in horror, providing a tale of how women are treated in society. With a limited budget, the filmmakers have done a commendable job of creating an engaging and thought-provoking story. The film has been well-received by audiences, with 2.3k IMDb users adding it to their watchlists.
Hollywood Movies in Telugu Dubbed Medusa: Beauty is the Beast is one of the many Hollywood movies in Telugu dubbed that caters to the growing demand for international content in the region. These dubbed versions allow Telugu audiences to enjoy popular Hollywood films in their native language, making them more accessible and engaging.
The rise of Hollywood movies in Telugu dubbed represents a significant shift in the region’s cinematic landscape. It not only broadens the range of entertainment options available to Telugu-speaking audiences but also fosters a greater understanding and appreciation of diverse storytelling techniques and cultural perspectives. The success of films like Medusa demonstrates that there is a receptive audience for international content, paving the way for more innovative and diverse cinematic experiences in the Telugu-speaking regions.
Now, let’s explore the sequel of Medusa, Medusa’s Venom.
Hollywood Movies in Telugu Dubbed
Medusa’s Venom – Hollywood movies in Telugu dubbed (2023) Medusa’s Venom is a sequel to Medusa: Beauty is the Beast and continues the story of the deadly snake-woman. In this instalment, the beast is back, and her venom is deadlier than ever. When newcomer Lola is welcomed into Medusa’s circle, she undergoes a ritual to bring her closer to her new sisters.
Unlike the first film, Medusa’s Venom takes a more straightforward approach to the horror genre. It depicts a group of snake women who are also sex workers, living in a caravan site that is now under the control of Medusa. This Hollywood movie in Telugu dubbed, explores the theme of power corrupting people, as the sanctuary from the previous film has become a place of control.
Released in 2023, Medusa’s Venom avoids the subtlety and layered storytelling of its predecessor, opting for a more direct and action-oriented narrative. The film continues the Greek mythology-inspired horror elements while delving deeper into the dynamics of the snake women’s group.
Hollywood movies in Telugu dubbed: A Growing Trend The success of Medusa: Beauty is the Beast and Medusa’s Venom highlights the growing trend of Hollywood movies in Telugu dubbed. This trend allows Telugu audiences to enjoy a wider range of international films, from action blockbusters to thought-provoking dramas.
As the demand for Hollywood movies in Telugu dubbed continues to rise, more and more filmmakers are recognizing the potential of this market. By adapting popular Hollywood films for Telugu audiences, they are able to reach a larger and more diverse viewership, while also showcasing the talent and creativity of the Telugu film industry.
Wrapping Up In conclusion, Medusa: Beauty is the Beast and Medusa’s Venom are two examples of the growing popularity of Hollywood movies in Telugu dubbed. These films offer a unique blend of horror, mythology, and social commentary, providing audiences with an engaging and thought-provoking viewing experience.
As the trend continues to evolve, it has the potential to influence local filmmaking practices, encourage cross-cultural exchanges, and ultimately enrich the Telugu film industry. We are excited to see what other Hollywood movies are adapted for Telugu audiences in the future, are you?
-
 @ fbf0e434:e1be6a39
2025-04-16 05:38:17
@ fbf0e434:e1be6a39
2025-04-16 05:38:17Hackathon 概要
由瑞士洛桑联邦理工学院(EPFL)区块链学生协会组织的 Privacy and Verifiability Hackathon 于 2023 年 3 月 8 日至 9 日成功举办。这场 26 小时极限挑战吸引 36 名开发者注册参与,最终提交 23 个获批项目,聚焦区块链隐私与可验证性技术解决方案开发,由 Mina、Hedera Hashgraph Association 及 Hylé 等机构赞助,总奖池达 15,000 美元。
显著的成就包括在隐私增强方法和可验证区块链解决方案方面的创新。项目的评估标准包括创新性、技术执行,以及在解决隐私和可验证性问题上的有效性。所展现的多样化解决方案突出显示了区块链领域的原创性和实用应用。
Hackathon 促进了学生、专业人士和爱好者之间的协作和创造力,推进了关于隐私和可验证区块链技术的讨论。活动强调了分散化解决方案在应对隐私挑战方面的潜力,进一步确认了社区在推动区块链创新方面的承诺。
Hackathon 获奖者
Privacy and Verifiability Hackathon 以超过 25 个项目竞争 15,000 美元奖池而告终。它展示了在隐私和验证技术中取得突破的创新解决方案,分为三个类别。
Mina 奖得主
- Mina Cash: 利用 Mina Protocol 的零知识证明进行匿名支付交易,确保链上证明和链下隐私。
- zkPetitions: 一种去中心化应用程序,使用零知识证明来保护隐私和数据完整性,并进行请愿处理。
- ZKribble.io: 一种利用零知识证明游戏,在绘制和猜测上下文中保护秘密词语。
- Aether ticket: 集成 Mina Protocol 的票务验证平台,通过零知识证明实现安全、私密的验证。
- Hush tag: 使用 Mina Protocol 的去中心化票务系统,实现安全和私密的票务生成与验证。
Hedera Hashgraph Association 奖得主
- AtlasID: 使用 React、Express 和 SD-JWT VC 技术实现注重隐私的身份验证。
- donate.fun: 通过区块链和身份验证来增强人道主义援助的透明度和安全性。
- Geotrust: 用于地理寻宝的网络应用程序,具备位置创建和稳健的用户验证功能。
- Hedemon: 使用 Hedera 区块链将实物收藏品转换为可验证真实性和隐私的 NFTs。
Hylé 奖得主
- Sthylé - image verification: 基于区块链的平台,用于验证图像真实性与管理。
- zkIA: 专注于 AI 应用中的零知识证明,尽管没有提供具体技术细节。
- CipherSocial: 通过去中心化平台使用密码学和区块链,基于兴趣将用户连接起来以保护隐私。
- Plethora: 用于创建使用零知识证明的 AI 代理,完成私密、可验证的任务。
有关项目的完整列表和更多详细信息,请访问 dorahacks.io 上的 Hackathon页面 。
关于组织者
Blockchain Student Association
Blockchain Student Association 旨在教育和吸引学生参与区块链技术领域。该组织以其在区块链系统和应用方面的专业知识而闻名,积极举办研讨会和工作坊以增强成员的技术理解。它曾与行业领导者合作开展项目,专注于创新的区块链解决方案。该组织的使命是培养一个探索区块链实际应用并在快速发展的领域内提升技术素养的知识社区。
-
 @ fbf0e434:e1be6a39
2025-04-16 05:38:05
@ fbf0e434:e1be6a39
2025-04-16 05:38:05Hackathon 概述
由 SUCI Blockchain Hub 主办、CodeX 赞助的 AI Hackathon 于 2025 年 3 月 7-9 日在越南胡志明市成功举办。这场线下活动吸引 42 名开发者参与,围绕实用场景的真实资产整合与 AI 代理开发,共诞生 12 个创新项目。
此次 Hackathon 总奖池为 15,000 美元,以 USDT 和 CDX 代币形式分配。一等奖获得者获得 4,000 USDT 和 2,000 CDX 代币,以及前往泰国参加即将举办的 COTI Foundation Hackathon 的旅行和住宿。第二名和第三名分别获得 3,000 和 2,000 USDT,以及 CDX 代币。特别赛道奖项包括最佳 AI 代理、最佳无代码解决方案和最佳真实应用,每项获得 1,000 USDT 和 500 CDX 代币。其他奖项则表彰了创新 AI 应用、跨行业解决方案和社区影响。
活动促进了交流、学习和协作创新,展示了 AI 与区块链技术之间日益紧密的联系。
Hackathon 获奖者
AI Hackathon 2025 展现了技术创新和各领域的创意。历经 48 小时,参与者密集合作解决问题,评选出在三个奖项类别中的杰出项目:主要奖项、赛道奖项和特别奖项。
主要奖项获奖者
以下三个项目因其创新和实施而脱颖而出:
- VocakeX:这是一款 Web3 教育科技平台,利用游戏化和 AI 增强学习,结合 AI 驱动模块与游戏化元素,提高教育参与度和学习保持率。
- StudyVerse:通过分析学生情绪,提供个性化的健康建议和学习指导,旨在通过情感识别和自适应反馈提升教育效果的 AI 平台。
- VaultAI:一款 AI 驱动的加密钱包,设计用于复杂的资产管理和 DeFi 洞察,利用分析和机器学习优化财务决策。
赛道奖项获奖者
项目因在 AI 代理、无代码解决方案和真实应用中的成就而被认可:
- CryptoMentor:一个智能聊天机器人,帮助新投资者学习和进行加密交易,提供实时 API 集成以便可靠的帮助。
- VaultAI
- Scholar AI:一款 AI 工具,通过数据分析为留学决策提供量身定做的教育和财务机会的推荐。
特别奖项获奖者
这些奖项凸显了具有创新潜力、跨行业应用和社区影响的项目:
- StudyVerse
- TourRecommendation:一种 AI 工具,通过区块链驱动的透明度帮助游客找到可靠的餐饮和住宿,提升交易的信任度。
- Buildlink:通过 AI 简化区块链交互,提供 NEAR 区块链上的用户友好互换和质押,提高新用户的可及性。
此次 Hackathon 强调了 AI 在应对复杂问题和提供跨领域影响力解决方案方面的能力。有关所有项目的更多详细信息,请访问 Dorahacks AI Hackathon。
关于组织者
SUCI BLOCKCHAIN HUB
SUCI Blockchain Hub 致力于区块链技术的开发和应用。该组织以推进各行业的安全去中心化解决方案而闻名,并对多个重要区块链项目作出了贡献。通过研究和开发,SUCI Blockchain Hub 促进创新,与行业领导者协作,提升区块链应用,推动数字交易的可及性和透明度。目前,组织的使命着重于扩展区块链整合,为企业和个人提供高效、安全的解决方案。
-
 @ 502ab02a:a2860397
2025-04-16 04:11:58
@ 502ab02a:a2860397
2025-04-16 04:11:58ในยุคที่ใครๆ ก็พูดเรื่อง สิทธิเสรีภาพ จะมีใครรู้บ้างว่า สิ่งที่เรากินทุกวัน กลับกำลังเข้าสู่ยุค ไร้สิทธิในการรับรู้ โดยเฉพาะเมื่อพูดถึงสิ่งที่เรียกว่า “GMO 2.0”
ใช่แล้วครับ GMO 2.0 หรือ synthetic biology ไม่ใช่ข้าวโพด BT, ไม่ใช่ถั่วเหลืองต้านยาฆ่าหญ้าแบบเดิม แต่มันคือ “พืชที่ถูกดัดแปลงพันธุกรรมแบบไม่มีรอยแผล” คือการใช้เทคโนโลยี CRISPR-Cas9, TALEN หรือ ZFN เข้าไป “ตัดต่อยีน” ภายในพืช โดยไม่ต้องใส่ยีนแปลกปลอมจากสิ่งมีชีวิตอื่น
ถ้าจำได้ ที่ผมเคยแชร์เรื่องการสร้างหมาป่า Game of Thrones และกำลังทำแมมมอธ อยู่นั่นละครับ CRISPR คือเทคโนโลยีที่เขาใช้ ผมเคยโพสไว้ว่า ผมสนใจเรื่องสัตว์นะ แต่ผมมีเรื่องกังวลควบคู่มาด้วย นี่คือเรื่องที่ผมบอกไว้ครับ
เพราะการสร้างสิ่งเหล่านั้นมันฟังดูดีใช่ไหมครับ? แต่ปัญหาคือ...มันดีจนไม่ต้องถูกเรียกว่า GMO นี่คือกลยุทธ์ใหม่ของอุตสาหกรรมพันธุ์พืช เพราะในหลายประเทศ เช่น สหรัฐฯ แคนาดา และแม้แต่ญี่ปุ่น กฎหมายไม่ถือว่า CRISPR เป็น GMO ถ้าไม่มีการนำยีนจากสิ่งมีชีวิตอื่นมาใส่เข้าไป
พูดง่ายๆ คือ “ตัดแต่งยีนจากของตัวเอง ยังไม่เรียกว่า GMO” แต่ผลที่ออกมา... อาจเปลี่ยนทั้งระบบการเติบโตของพืช เปลี่ยนลักษณะอาหาร เปลี่ยนภูมิคุ้มกัน และเปลี่ยนการควบคุมอำนาจในห่วงโซ่อาหารโลก
แล้วการที่ไม่ต้องติดฉลาก ไม่ต้องแจ้งผู้บริโภค นี่คือสาระสำคัญ!!!! เพราะเมื่อมันไม่ใช่ GMO ในทางกฎหมายก็ไม่มี “ภาระในการแจ้งผู้บริโภค” ใครกินพืช CRISPR เข้าไป ก็จะไม่รู้เลยว่า...นี่คือพันธุ์ที่ผ่านการดัดแปลงระดับ DNA มาแล้ว
ลองคิดดูครับว่า นี่เรากำลังถูกดันเข้าสู่ยุคที่ “มะเขือเทศหวาน” หรือ “ข้าวที่แข็งแรงทนแล้งดี” หรือ "พืชที่สะสมโปรตีนวิตามินที่ใส่สารละลายไว้ในตัว" อาจจะผ่านการตัดต่อพันธุกรรม แต่คุณไม่มีทางรู้ เพราะมันไม่มีทางตรวจพบจากฉลาก หรือการทดสอบดีเอ็นเอปกติ
คำถามคือ ใครควบคุม? ใครได้ประโยชน์? คำตอบเหมือนเดิมละครับ บริษัทยักษ์ใหญ่ที่จดสิทธิบัตรไว้ก่อนไง 5555
ในระบบ GMO 1.0 อุตสาหกรรมเคยพยายามผูกขาดพันธุ์โดยใช้สิทธิบัตร แต่ผู้บริโภคยังสามารถรู้และต่อต้านได้ แต่ GMO 2.0 มาแบบ “เงียบกว่า แหลมคมกว่า และควบคุมง่ายกว่า”
ยกตัวอย่างเช่น ข้าวโพด CRISPR จากบริษัท Corteva (เจ้าของเดิมคือ DowDuPont) สามารถสร้างพันธุ์ที่ “โตไว แห้งเร็ว เก็บเกี่ยวได้เร็วกว่าเดิม” แต่พันธุ์นี้มีสิทธิบัตรคุ้มครองแบบเบ็ดเสร็จ แถมไม่มีข้อผูกมัดในการแจ้งข้อมูลกับผู้บริโภคด้วย
ในส่วนของความเสี่ยงที่ใครก็ไม่กล้าพูดถึงก็มีอีกนะครับ เช่น -การตัดต่อยีนแม้จะไม่ใส่ยีนใหม่ แต่ก็สามารถเกิด off-target effect หรือผลกระทบที่ไม่ได้ตั้งใจได้ -ยีนที่ถูกตัดออกอาจมีหน้าที่สำคัญด้านภูมิคุ้มกันหรือสมดุลภายในพืช ซึ่งส่งผลถึงโภชนาการของผู้บริโภค -การกระจายของพันธุ์ CRISPR โดยไม่ต้องผ่านการควบคุม อาจทำให้พืชดั้งเดิม สูญพันธุ์ทางพันธุกรรม เพราะถูกแทนที่แบบเงียบๆ
แล้วเกษตรกรล่ะ? จะรอดไหม? คำตอบคือ รอดยากขึ้นครับ หรือจะเรียกไม่มีทางรอดดีโหดไปไหม? เพราะ GMO 2.0 ไม่ใช่แค่เรื่องการดัดแปลงพันธุกรรม ถ้ามองภาพกว้างกว่านั้น มองโครงสร้างเลยนี่มันคือการสร้าง “ระบบใหม่ในการผูกขาดพันธุ์” ที่มองไม่เห็น เป็นการล็อกพันธุ์พืชด้วย “สิทธิบัตรโมเลกุล” ซึ่งเกษตรกรไม่สามารถเซฟพันธุ์ไว้ปลูกต่อได้ เพราะละเมิดกรรมสิทธิ์ ต้องเช่าใช้หรือ subscribe ไปตลอดชีวิต มีหน้าที่แค่หน่วยปลูกเท่านั้น
ขณะที่พันธุ์พื้นบ้านหรือพันธุ์เปิดกลับไม่สามารถแข่งขันกับพันธุ์ดัดแปลงเหล่านี้ได้เลย เพราะถูกออกแบบมาให้ “ตอบโจทย์ตลาด” แต่ไม่ใช่ “ตอบโจทย์ดินฟ้าอากาศจริงๆ” แบบเกษตรวิถีเดิม
แล้วในโลกหลัง GMO 2.0 จะเหลืออะไรให้เราปลูก? นี่ไม่ใช่การต่อต้านเทคโนโลยีนะครับ ทุกคนเข้าใจดีว่าเราต้องเติมโตและมีการพัฒนา แต่คือคำถามเรื่อง สิทธิในการรู้ สิทธิในการเลือก และ สิทธิในการรักษาพันธุกรรมของพืชพื้นบ้าน มันอยู่ตรงไหนก่อน
เพราะเมื่อเราถูกเปลี่ยนพันธุ์แบบไม่รู้ตัว วันหนึ่ง เราอาจต้องซื้อเมล็ดพันธุ์ทุกปีจากบริษัทเพียงไม่กี่ราย ปลูกอาหารในระบบที่เราควบคุมไม่ได้ และกินอาหารที่ไม่มีใครกล้ารับรองว่า “ดั้งเดิม” จริงหรือเปล่า
ดังนั้นมันจึงถึงเวลาตั้งคำถามใหม่... ว่า real food ของเรายัง real อยู่ไหม?
ในยุคที่แม้แต่มะเขือเทศก็ถูกเปลี่ยนยีน และข้าวโพดก็ถูกออกแบบมาให้เก็บเกี่ยวเร็วขึ้น แต่ไม่งอกได้อีกเลย คำถามไม่ใช่แค่ “อร่อยไหม” หรือ “หวานแค่ไหน” แต่คือ
“เราเหลือสิทธิ์อะไรกับอาหารที่เราปลูกบ้าง?”
สิ่งนี้มันเกิดขึ้นไปแล้วครับ นี่ยังไม่ได้พูดถึงผลกระทบจากการกิน เพราะมีหลายๆคนแฮปปี้ดี๊ด๊าไปมากมาย กับสตอเบอรี่หวานฉ่ำ เมลลอนหอมฉุย กล้วยใบงาม กินแล้ว "healthyyyyy" อะตรงนั้นผมไม่แย้งแล้วกัน
ซีรีย์นี้เลยให้มองผลของการถูกจองจำครับ กบชอบอาบน้ำอุ่นเสมอ
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-
 @ 8e7e2128:25e34fd1
2025-04-16 05:20:11
@ 8e7e2128:25e34fd1
2025-04-16 05:20:11In today’s beauty-driven, fast-paced world, the desire for youthful, radiant skin is stronger than ever. But unlike in decades past, where cosmetic surgery reigned supreme, modern skincare enthusiasts are increasingly turning toward gentler alternatives. Enter the era of minimally invasive skin treatments—solutions designed to refresh and rejuvenate without the need for scalpels, sutures, or significant downtime.
Among the many advancements, one technology stands out: light-based skin therapy. From acne to aging, pigmentation to inflammation, light is proving to be one of the most versatile tools in the modern skincare toolkit. But how did we get here, and what exactly makes these treatments so popular? Let’s break it all down.
Why Minimally Invasive Is the New Gold Standard Once upon a time, surgical facelifts and chemical peels were the go-to methods for anyone looking to turn back the clock on aging. But as our understanding of skin biology has evolved—and with the rise of social media and wellness culture—people are now seeking treatments that align with a lifestyle of balance, subtlety, and self-care.
Here’s why minimally invasive skin treatments are dominating the skincare space: - Little to no downtime: You can schedule a session on your lunch break and head back to work without skipping a beat. - Natural results: These treatments work with your body’s own processes to gradually enhance your skin’s appearance. - Lower risk: With no need for general anesthesia or extensive recovery, the risk profile is significantly lower. - Affordability: Compared to surgical options, many of these treatments are easier on the wallet. - Customization: Providers can tailor treatments based on individual skin types, concerns, and goals.
A Closer Look at the Technology: Light-Based Skin Therapy At the forefront of this skincare revolution is light-based skin therapy, a non-invasive category of treatments that use controlled light wavelengths to trigger natural biological processes within the skin.
How Does It Work? Different wavelengths of light penetrate the skin at various depths. By targeting specific skin layers, light-based skin therapy can: Stimulate collagen production Kill acne-causing bacteria Reduce pigmentation Promote healing and tissue regeneration
There’s no cutting, no abrasion, and often no pain—just the gentle power of light doing what it does best.
Types of Light-Based Skin Therapy Let’s dive into the most popular forms of light-based therapies and what they can do for your skin.
1. LED Light Therapy LED therapy is one of the most accessible and gentle treatments available. It involves the application of different colored lights to target various skin concerns: Blue light: Effective for killing Propionibacterium acnes, the bacteria behind acne breakouts. Red light: Boosts circulation and stimulates collagen production, making it ideal for anti-aging. Green light: Targets hyperpigmentation and sun damage. Yellow light: Helps reduce redness and inflammation. LED therapy can be done in-office or at home with wearable LED masks and handheld devices.
2. IPL (Intense Pulsed Light) Often referred to as a “photofacial,” IPL delivers broad-spectrum light deep into the skin. It’s especially effective for: Sunspots and age spots Redness and rosacea Broken capillaries Uneven skin tone Unlike lasers, which use a single wavelength, IPL uses multiple wavelengths, allowing for treatment of multiple issues in a single session.
3. Fractional Lasers Fractional lasers are more intensive than LED or IPL, but they’re still considered minimally invasive. They work by creating microscopic columns of controlled damage in the skin, which stimulates the body’s natural healing response. These are best for: Acne scars Fine lines and wrinkles Stretch marks Skin resurfacing
Downtime can vary, but results are often dramatic and long-lasting.
4. Photodynamic Therapy (PDT) A more medical-grade form of light-based skin therapy, PDT combines a light-sensitive solution with a specific wavelength of light to treat more severe issues, such as: • Precancerous skin lesions (actinic keratosis) • Severe acne • Sun damage This treatment is typically performed by dermatologists and offers both therapeutic and cosmetic benefits.
What to Expect During and After Treatment One of the key reasons minimally invasive treatments have taken off is how user-friendly they are. Here’s a general outline of what most patients can expect:
Before the Treatment: A consultation to assess your skin and recommend the right therapy. Photos may be taken for progress tracking. Skin will be cleansed, and protective eyewear provided (for light-based therapies).
During the Treatment: Most treatments are painless or involve minimal discomfort. Sessions usually last 15 to 60 minutes, depending on the area and technique.
After the Treatment: Mild redness or warmth is common but usually resolves within hours. You may be advised to avoid sun exposure and use gentle skincare. Results typically build over several sessions.
Is It Right for You? If you’re looking for a skin boost without the risks or recovery time of surgery, light-based skin therapy and other minimally invasive treatments could be perfect for you. These therapies are suitable for a wide range of concerns and skin types, but it’s always best to consult with a certified dermatologist or aesthetician to ensure you’re getting the safest and most effective treatment plan.
The Future of Skincare Is Bright—Literally As technology advances and consumer demand for safer, more effective skin care grows, light-based skin therapy is becoming a cornerstone of modern aesthetic medicine. These treatments blend the best of science and beauty, offering real results without drastic measures. Whether you're tackling acne, sun damage, or simply aiming to maintain your youthful glow, the future of skincare is about enhancement, not overhaul. So say goodbye to invasive procedures—and hello to glowing skin, one light beam at a time.
The rise of minimally invasive skin treatments has redefined what it means to age gracefully. By prioritizing natural results, minimal recovery, and long-term skin health, these therapies are changing lives (and complexions) one session at a time.
And when it comes to harnessing the power of light, light-based skin therapy is illuminating the way forward—proving that sometimes, the best treatments are the ones that don’t require going under.
-
 @ 502ab02a:a2860397
2025-04-16 04:06:25
@ 502ab02a:a2860397
2025-04-16 04:06:25"Satoshi is not me." #ตัวหนังสือมีเสียง
เพลงนี้เรียกได้ว่าเป็นจุดเริ่มต้นของคอนเสปอัลบั้มนี้เลยครับ ผมเลยเอาชื่อเพลงนี้เป็นชื่ออัลบั้มไปด้วย
มันเริ่มจากการที่คนชอบคาดคะเนกันไปว่า ใครคือ satoshi nakamoto ตัวจริง แล้วก็มีสารพัดทฤษฎีออกมา ค้นคว้ากันไปถึง กระทู้ที่คุยกันใน mailing list สมัยนั้นเลยเชียว
มีคนนึงที่ไม่พลาดโดนมองว่าเป็น satoshi นั่นคือ Jack Dorsey (nostr:npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m) ผู้ร่วมก่อตั้ง twitter แล้วยิ่งเขาลงมาในทุ่งม่วงและสนับสนุน บิทคอยน์ เต็มตัวรวมถึงไปร่วมงานคอนเฟอร์เรนซ์บิทคอยน์ด้วย นั่นยิ่งทำให้คนพูดกันหนาหูขึ้น
ในปี 2020 Dorsey ได้ให้สัมภาษณ์กับ Lex Fridman โดยเมื่อถูกถามว่าเขาคือ Satoshi Nakamoto หรือไม่ เขาตอบว่า "ไม่ และถ้าผมเป็น ผมจะบอกคุณไหมล่ะ?"
นี่หละครับ ประโยคที่ผมรู้สึกว่า น่ารักและเอามาขยายความเป็นความจั๊กจี้ได้โรแมนติกดี แถมมันเข้ากับประโยคที่พวกเรามักใช้ว่า we’re all Satoshi
ทำให้คำว่า Satoshi is not me เลยกลายเป็นมุมกลับที่จั๊กจี้ดี ในความคิดผม
ผมเลยเริ่มจากการร่างไว้ว่า ท่อนฮุคของเพลงจะต้องมีคำว่า "Satoshi is not me" บังคับตัวเองไว้ก่อนเลย ฮาๆๆๆ
เพลงจะกล่าวถึงบรรยากาศโรแมนติกสบายๆผ่อนคลาย หนุ่มสาวเดินไปตามชายหาดด้วยกัน หัวเราะหยอกล้อ
เนื้อเพลงพยายามซ่อนการเปรียบเทียบเป็นนัยยะ ตามความต้องการแรกในการทำอัลบั้มนี้คือ ถ้าไม่โดนยาส้มไว้ ก็ยังฟังได้แบบสบายๆ ตามประสาเพลงบอสซาทั่วไป แต่ถ้าโดนยาส้มแล้ว อาจจะฟังแล้วรู้สึกถึงอีกมุมที่เป็นปรัชญาบิทคอยน์ได้
เรียกว่าไม่อยากเอา core code มาเขียนเพลงนั่นละครับ
เราเริ่มด้วยการวางฉากให้สบายๆชายทะเล ประสาความบอสซาโนวาก่อน ด้วยท่อนแรก In the cool of evening, beneath the twilight trees, We sway with the ocean, feeling the summer breeze, There's a whisper in the air, oh so tender, so free, ยามเย็นอ่อนลม ใต้พฤกษาเวลาโพล้เพล้ เราสองตระกองกอดไปกับคลื่นทะเล ลมฤดูร้อนพัดพาเสียงเล่าเบา ๆ
ก่อนจะลงท่อนปิดด้วยประโยคว่า You smile and softly whisper, "Satoshi is not me." เธอยิ้มแล้วกระซิบว่า "ฉันไม่ใช่ซาโตชิ"
แต่ผมก็ยังพยายามแทรกเรื่องของบิทคอยน์และเบื้องหลัง fiat money เอาไว้ด้วยนิดนึง Soft waves kiss the sand, like a gentle dream, With every step we take, there's a secret melody, คลื่นเคล้าหาดเบา ๆ ดุจฝันที่ละมุนละไม ทุกก้าวที่เราย่างไว้ ล้วนมีท่วงทำนองแอบแฝงอยู่ ฮาๆๆๆ คือกำลังพยายามบอกว่า ความราบรื่นในชีวิตเราทุกวันนี้ เราอาจรู้สึกสวยงาม แต่จริงๆแล้วทุกๆก้าวย่างของเรา ถูกกำหนดด้วยความลับบางอย่างอยู่
จากนั้นก็ปูเข้าสู่ทางรอด คล้ายๆกับชักชวนมาสร้างโลกที่หลุดพ้นจาก fiat In the world we're crafting, where our hearts feel light, We find our own rhythm, in the still of the night, No need for grand illusions, or some wild decree, มาระบายเมืองด้วยสีสันที่สดใสด้วยหัวใจแห่งเสรี เราสร้างท่วงทำนองของเรา แล้วเต้นใต้เงาจันทร์ จนแสงรุ่งทาบฟ้าอีกครา ไม่จำเป็นต้องมีมหากาพย์ภาพลวงตา หรือประกาศิตอันยิ่งใหญ่ใด
ก่อนจะจบผมวางท่อง bridge ไว้โดยมีประโยคว่า No chains to bind us, just a heartfelt plea, ไร้พันธนาการใดมาควบคุมเรา มีเพียงคำขอเบา ๆ จากใจที่แท้จริง เพื่อแสดงความปลดแอกอะไรบางอย่าง
ทีนี้ยังมีลูกเล่นในแต่ละท่อน ที่ใช้คำว่า "Satoshi is not me." ด้วยนะครับ ผมเอามาเรียงกันให้ตามนี้ You smile and softly whisper, "Satoshi is not me."
You laugh and then you tell me, "Satoshi is not me."
With your hand in mine, love, "Satoshi is not me."
You softly keep reminding, "Satoshi is not me."
Embrace the simple truth, “Satoshi is not me.”
คือเป็นการหยอดความโรแมนติกนิดหน่อย ว่าเชื่อเค้าเหอะนะ เค้าไม่ใช่ Satoshi ด้วยการใช้ประโยคต้นที่ขยับแรงขอร้องมากขึ้นเรื่อยๆ
หวังว่าหลังจากนี้เวลาฟังเพลงนี้จะจั๊กจี้แบบที่ผมนึกสนุกตอนเขียนนะครับ ฮาๆๆๆๆ 🎶 youtube music https://youtu.be/g8oyZQ_lTa0?si=kS7ga_TxmFnPOmwR
🟢 spotify https://open.spotify.com/track/69GOSGMrma3BONKG8l5wpN?si=c0e6711c7a994011
💽 tiktok ค้นหา Heretong Teera Siri เลือกแผ่นเสียงไปทำคลิปได้เลยครับ
Lyrics : Satoshi is not me [Verse] In the cool of evening, beneath the twilight trees, We sway with the ocean, feeling the summer breeze, There's a whisper in the air, oh so tender, so free, You smile and softly whisper, "Satoshi is not me."
[Vers 2] We walk along the shoreline, while the stars start to gleam, Soft waves kiss the sand, like a gentle dream, With every step we take, there's a secret melody, You laugh and then you tell me, "Satoshi is not me."
[Chorus] In the world we're crafting, where our hearts feel light, We find our own rhythm, in the still of the night, No need for grand illusions, or some wild decree, With your hand in mine, love, "Satoshi is not me."
[Verse 3] Let’s paint the town in colors, of freedom and delight, Dance in moonlit shadows, till the break of daylight, In this realm of wonder, where we both can be, You softly keep reminding, "Satoshi is not me."
[Bridge] Beneath the starlit canopy, where dreams softly align, We live for the moment, leave the rest behind, No chains to bind us, just a heartfelt plea, Embrace the simple truth, “Satoshi is not me.”
[Chorus] In the world we're crafting, where our hearts feel light, We find our own rhythm, in the still of the night, No need for grand illusions, or some wild decree, With your hand in mine, love, "Satoshi is not me."
pirateketo #siripun
-
 @ 8d34bd24:414be32b
2025-04-16 03:48:30
@ 8d34bd24:414be32b
2025-04-16 03:48:30Ever since becoming a Christian, I have whole-heartedly believed the Bible and that God will fulfill what He has promised. On the other hand, for the majority of the time I have been a Christian, I have dreaded reading prophecy. It seemed so hard to understand. Some is couched in figurative language, but I now believe much of it was hard to understand because there were no words for the technology and systems that would come into being and fulfill these predictions.
Now reading End times prophecy, like in Revelation, Daniel, Matthew 24-25, 2 Thessalonians, Zechariah, etc. the prophecies are starting to sound like the evening news instead of some poetic mystery. These predictions are making more and more sense as the technology and world politics begin to align with the prophecies. I have gone from hating when I get to prophecy passages, especially Revelation, in my Bible reading, to spending extra time reading these passages and seeing how they line up and clarify each other. (I really want to start a project linking all of the end-times prophetic passages together to see how they clarify each other and try to see the big picture, but that is a massive project and time is in short supply. The only way I know to do it is in Excel, but that isn’t efficient. If anyone has a suggestion for a better way to link and show relationships, I’d love to hear about it, especially if it is free or very cheap.)
Matthew recounts Jesus telling His disciples about what to expect in the end times. Although Matthew 24 describes more of the details of the events that happen, this passage in Matthew 25 describes the importance of watching expectantly for the signs of the times, so we are ready.
“Then the kingdom of heaven will be comparable to ten virgins, who took their lamps and went out to meet the bridegroom. Five of them were foolish, and five were prudent. For when the foolish took their lamps, they took no oil with them, but the prudent took oil in flasks along with their lamps. Now while the bridegroom was delaying, they all got drowsy and began to sleep. But at midnight there was a shout, ‘Behold, the bridegroom! Come out to meet him.’ Then all those virgins rose and trimmed their lamps. The foolish said to the prudent, ‘Give us some of your oil, for our lamps are going out.’ But the prudent answered, ‘No, there will not be enough for us and you too; go instead to the dealers and buy some for yourselves.’ And while they were going away to make the purchase, the bridegroom came, and those who were ready went in with him to the wedding feast; and the door was shut. Later the other virgins also came, saying, ‘Lord, lord, open up for us.’ But he answered, ‘Truly I say to you, I do not know you.’ Be on the alert then, for you do not know the day nor the hour. (Matthew 25:1-13) {emphasis mine}
Many Christians think studying prophecy is not useful for today, but that is not true. Our time is short and Jesus warned us to be aware and ready. We can’t be ready for something if we know nothing about it.
In this passage it mentions that “while the bridegroom was delaying, they all got drowsy and began to sleep.” How often do we feel the delay and begin to rest or get distracted by other things? Most Christians do not live like Christ’s return is imminent. Although we can’t know the hour or the day, we can know that we are closer to that hour than we have ever been before. Peter warns us not to doubt Christ’s coming or to become focused solely on our earthly lives.
Know this first of all, that in the last days mockers will come with their mocking, following after their own lusts, and saying, “Where is the promise of His coming? For ever since the fathers fell asleep, all continues just as it was from the beginning of creation.” (2 Peter 3:3-4)
Because Jesus has not returned for almost 2,000 years, many act as if He will never come, but that long wait instead suggests the time is nearing because God never breaks His promises.
For when they maintain this, it escapes their notice that by the word of God the heavens existed long ago and the earth was formed out of water and by water, through which the world at that time was destroyed, being flooded with water. But by His word the present heavens and earth are being reserved for fire, kept for the day of judgment and destruction of ungodly men.
But do not let this one fact escape your notice, beloved, that with the Lord one day is like a thousand years, and a thousand years like one day. The Lord is not slow about His promise, as some count slowness, but is patient toward you, not wishing for any to perish but for all to come to repentance. (2 Peter 3:5-9) {emphasis mine}
The long wait is due to God’s unfathomable mercy and patience, but we should also realize that the increase of evil in the world cannot continue forever. How much more can evil increase before mankind destroys itself? God claims judgement for Himself and finds every kind of sin abhorrent. If we are distraught over the sin in the world today, how much more awful is it to a holy, perfect God to see His very own creation destroyed by sin?
Just as the ten virgins became tired waiting, we tend to get caught up in the things of this world instead of focusing on God’s plan for us and the world. We act as if this world is the only thing we will experience instead of preparing for our rapture to heaven. We focus on our job, our homes, and our families (all good things) and miss the most important things — winning souls for heaven.
Just as Jesus gently reprimanded Martha for having the wrong focus:
But Martha was distracted with all her preparations; and she came up to Him and said, “Lord, do You not care that my sister has left me to do all the serving alone? Then tell her to help me.” But the Lord answered and said to her, “Martha, Martha, you are worried and bothered about so many things; but only one thing is necessary, for Mary has chosen the good part, which shall not be taken away from her.” (Luke 10:40-42) {emphasis mine}
In the same way, we get focused with the business of life and miss the most important stuff. It wasn’t bad of Martha to take care of her guests, but sitting with Jesus and learning from Him was more important. In the same way, our jobs, families, and homes are good things and we should do them well, but reading our Bibles, praying, growing closer to Jesus, and sharing the Gospel with those who don’t know Jesus is better.
When we believe that our time on earth is short and Jesus is coming for us soon, we are more likely to focus on the most important things — the eternal things.
This passage in Matthew 16 describes the importance of us knowing, understanding, and looking for the signs of the times.
The Pharisees and Sadducees came up, and testing Jesus, they asked Him to show them a sign from heaven. But He replied to them, “When it is evening, you say, ‘It will be fair weather, for the sky is red.’ And in the morning, ‘There will be a storm today, for the sky is red and threatening.’ Do you know how to discern the appearance of the sky, but cannot discern the signs of the times? An evil and adulterous generation seeks after a sign; and a sign will not be given it, except the sign of Jonah.” And He left them and went away. (Matthew 16:1-4) {emphasis mine}
Christians that believe studying end times prophecy is not important would be rebuked even today by Jesus. We are supposed to study and learn and prepare and watch eagerly for His return.
In Revelation, God says we are blessed if we hear and heed the words of this prophecy.
The Revelation of Jesus Christ, which God gave Him to show to His bond-servants, the things which must soon take place; and He sent and communicated it by His angel to His bond-servant John, who testified to the word of God and to the testimony of Jesus Christ, even to all that he saw. Blessed is he who reads and those who hear the words of the prophecy, and heed the things which are written in it; for the time is near. (Revelation 1:1-3) {emphasis mine}
Do you seek God’s blessing? Then study God’s prophecies, especially as written in Revelation. God is good and He has shown His children what will happen, so they can be prepared. Don’t be like the five foolish virgins who were unprepared. Study the Scriptures. Look for the signs. Be ready for our Savior’s return by inviting as many people as possible to join us.
Trust Jesus.
FYI, I hope to write several more articles on the end times (signs of the times, the rapture, the millennium, the judgement, etc.).
-
 @ 35f80bda:406855c0
2025-04-16 03:11:46
@ 35f80bda:406855c0
2025-04-16 03:11:46O Bitcoin Core 29.0 foi oficialmente lançado e traz diversas melhorias técnicas voltadas para desenvolvedores, operadores de full nodes e a comunidade Bitcoin mais técnica. Desde mudanças na camada de rede até a atualização do sistema de build, este release é um passo significativo na modernização do ecossistema.
Se você roda um full node, desenvolve software que interage com o Core via RPC ou apenas quer estar por dentro das novidades técnicas, este artigo é para você.
Alterações na Rede e no P2P
Suporte ao UPnP Removido O UPnP foi totalmente desativado por razões de segurança e manutenção. Agora, a recomendação é utilizar a flag -natpmp, que conta com uma implementação interna de PCP e NAT-PMP. Mais seguro e mais leve.
Melhorias no Suporte Tor A porta onion agora é derivada da flag -port, permitindo múltiplos nós Tor na mesma máquina — ótimo para quem opera ambientes de teste ou múltiplos peers.
Transações Órfãs com Propagação Aprimorada O node agora tenta buscar os parents de transações órfãs consultando todos os peers que anunciaram a transação. Isso ajuda a preencher lacunas na mempool de forma mais eficiente.
Mempool e Política de Mineração
Ephemeral Dust Introdução de um novo conceito: ephemeral dust, que permite uma saída "dust" gratuita em uma transação desde que ela seja gasta dentro do mesmo pacote. Pode ser útil para otimizações de fees.
Correção no Peso Reservado de Blocos Bug que causava duplicação de peso reservado foi corrigido. Agora existe a flag -blockreservedweight, com limite mínimo de 2000 WU.
RPCs e REST mais robustos
- testmempoolaccept agora fornece o campo reject-details.
- submitblock preserva blocos duplicados mesmo que tenham sido podados.
- getblock, getblockheader e getblockchaininfo agora incluem o campo nBits (alvo de dificuldade).
- Novo RPC: getdescriptoractivity, que permite ver atividades de descritores em intervalos de blocos.
- APIs REST agora retornam nBits também no campo target.
Sistema de Build Modernizado
Uma das mudanças mais bem-vindas: o Bitcoin Core agora usa CMake em vez de Autotools como padrão de build. Isso facilita integração com IDEs, CI/CD pipelines modernos e personalização do build.
Outras Atualizações Importantes
- -dbcache teve limite máximo reduzido para lidar com o crescimento do conjunto UTXO.
- O comportamento Full Replace-by-Fee (RBF) agora é padrão. A flag -mempoolfullrbf foi removida.
- Aumentaram os valores padrão de -rpcthreads e -rpcworkqueue para lidar com maior paralelismo.
Ferramentas Novas
Uma nova ferramenta chamada utxo_to_sqlite.py converte snapshots compactos do conjunto UTXO para SQLite3. Excelente para quem quer auditar ou explorar o estado da blockchain com ferramentas padrão de banco de dados.
Limpeza de Dependências
As bibliotecas externas MiniUPnPc e libnatpmp foram removidas, substituídas por implementações internas. Menos dependências = manutenção mais fácil e menos riscos.
Como atualizar?
- Pare o seu nó atual com segurança.
- Instale a nova versão.
- Verifique configurações como -dbcache, -blockreservedweight e o comportamento RBF.
- Consulte os logs com atenção nas primeiras execuções para validar o novo comportamento.
Conclusão
O Bitcoin Core 29.0 representa um passo firme em direção a uma base de código mais moderna, segura e modular. Para quem mantém nós, desenvolve soluções sobre o Core ou audita a rede, é uma atualização que vale a pena testar e entender a fundo.
Já testou a nova versão? Notou impactos nas suas aplicações ou infraestrutura?
Referências
-
 @ 35da2266:15e70970
2025-04-16 03:45:13
@ 35da2266:15e70970
2025-04-16 03:45:13Qd6Vc1ZwkoV314qozv8RVkBk0YW9XQK38bjizGI5a4ws0wuuJQR5U0uDEzKcNd9/QWPbaj4rQIgdFNlmmybdn4s1WXfmdoymUFBRjpBau7Nj2yeXaKtk+RVl488Kxo0/kb13hQfX8q6kzPs9jY2NWS9KedXA+LSEhZJKXeXn5lT8hxuFPc6Q/rmVQT3gTRAORK/LUizNE71+wnaJPV0V/mNrdiKxWbFAv6lnmSPY+zKVY/u5E6vgjgObaSGpjj+MOaMkYfGxnm7fm9kvQawJNmIHdYn2CcymnSYHhuL7jqohECqf0DtPrewYkFfJ6mrerKhKwRbaHRIOcOJKiIjw5Q==?iv=RdYmRey3pCxDafHJpDdFVA==
-
 @ c13fd381:b46236ea
2025-04-16 03:10:38
@ c13fd381:b46236ea
2025-04-16 03:10:38In a time of political volatility and declining public trust, Australians are looking for leaders who don’t just talk about accountability—but prove it. It’s time for a new standard. A protocol that filters for competence, responsibility, and integrity—not popularity alone.
Here’s the idea:
Anyone who wants to run for public office in Australia must stake 100Ksats to a public address and maintain provable control of the corresponding private key for the duration of their term.
A Low Barrier With High Signal
The amount—100Ksats—is modest, but meaningful. It isn’t about wealth or exclusion. It’s about signal. Controlling a private key takes care, discipline, and a basic understanding of digital responsibility.
This protocol doesn't reward those with the most resources, but those who demonstrate the foresight and competence required to secure and maintain something valuable—just like the responsibilities of public office.
How It Works
This system is elegantly simple:
- To nominate, a candidate generates a keypair and deposits 100Ksats into the associated address.
- They publish the public key alongside their candidate profile—on the electoral roll, campaign site, or an independent registry.
- Throughout their time in office, they sign periodic messages—perhaps quarterly—to prove they still control the private key.
Anyone, at any time, can verify this control. It’s public, permissionless, and incorruptible.
Why This Matters
Private key management is more than technical—it’s symbolic. It reflects:
- Responsibility – Losing your key means losing your ability to prove you’re still accountable.
- Integrity – Key control is binary. Either you can sign or you can’t.
- Long-term thinking – Good key management mirrors the strategic thinking we expect from leaders.
This isn’t about promises. It’s about proof. It moves trust from words to cryptographic reality.
A Voluntary Standard—for Now
This doesn’t require legislative change. It can begin as a voluntary protocol, adopted by those who want to lead with integrity. The tools already exist. The expectations can evolve from the ground up.
And as this becomes the norm, it sets a powerful precedent:
"If you can’t manage a private key, should you be trusted to manage public resources or national infrastructure?"
Identity Without Surveillance
By linking a public key to a candidate’s public identity, we create a form of digital accountability that doesn’t rely on central databases or invasive oversight. It’s decentralized, simple, and tamper-proof.
No backdoors. No bureaucracy. Just Bitcoin, and the competence to manage it.
Bitcoin is the foundation. Asymmetric encryption is the filter.
The result? A new class of public leaders—proven, not promised.Let’s raise the standard.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ d5c3d063:4d1159b3
2025-04-16 03:01:47
@ d5c3d063:4d1159b3
2025-04-16 03:01:47เคยได้ยินคำนี้ไหมครับ… You will own nothing and you will be happy คุณจะไม่มีอะไรเลย แล้วคุณจะมีความสุข
ฟังดูดีเนอะ เหมือนจะสอนให้ไม่ยึดติดอะไร หลายคนเลยบอกว่า เฮ้ย! นี่มันพุทธเลยนี่หว่า เพราะพุทธก็บอกว่าให้ปล่อยวาง ไม่ต้องยึดอะไร แต่เดี๋ยวก่อนนะ...มันใช่แนวพุทธจริงๆ เหรอ .
พุทธไม่เคยบอกให้เราทิ้งทุกอย่าง
แต่แค่เตือนว่าสิ่งที่เรามีมันอยู่กับเราไม่นาน ยิ่งยึดไว้แน่นเท่าไหร่...ก็ยิ่งทุกข์มากเท่านั้น . มีบ้าน มีเงิน มีรถ มีของที่ชอบ ไม่มีปัญหาเลย แต่พุทธแค่เตือนว่า ของพวกนี้ไม่เที่ยง สักวันมันก็ต้องจากไป . ปัญหาไม่ใช่การมี แต่คือการยึดติด กลัวจะเสียมันไป พอเรากลัวมาก เราก็ทุกข์ ทุกข์จากการเสียดาย ทุกข์จากการอยากมีอยากได้มาก ทุกข์จากการไปเปรียบเทียบกับคนอื่น เพราะงั้น...จะมีอะไรก็ได้ แค่เข้าใจไว้ว่ามันไม่ได้อยู่กับเราไปตลอดก็พอแล้ว นี่แหละที่เรียกว่ามีด้วยปัญญา
แล้วที่บอกว่า You will own nothing and you will be happy ก็มาจากแนวคิดของ World Economic Forum เขาพูดถึงโลกอนาคต ว่า...คุณจะ -ไม่ต้องมีรถ เพราะเช่าใช้ผ่านแอปได้ -ไม่ต้องมีบ้าน เพราะเช่า(ผ่อน)ไปตลอดชีวิต -ไม่ต้องมีของใช้ เพราะรัฐจะจัดการให้หมด ฟังดูสะดวกเนอะ...แต่คำถามคือ… แล้วของทั้งหมดนั่น ใครเป็นเจ้าของ ถ้าเราไม่มีสิทธิเป็นเจ้าของอะไรเลย แล้วถ้าวันหนึ่ง เจ้าของนั้น เขาไม่ให้เราใช้ล่ะ เราจะทำยังไง . พุทธสอนให้พึ่งพาตนเอง อตฺตา หิ อตฺตโน นาโถ ตนเป็นที่พึ่งแห่งตน เพราะอิสรภาพที่แท้จริง คือการได้ใช้ปัญญาและตัดสินใจเองในชีวิตของเรา ไม่ใช่ปล่อยให้รัฐ หรือกลุ่มอำนาจใด ๆ คิดแทนเราในทุกเรื่อง
สอดคล้องกับแนวคิด Libertarianism ที่เชื่อว่า... ชีวิต เสรีภาพ และทรัพย์สิน คือสิทธิพื้นฐานที่รัฐไม่ควรละเมิด เพราะเสรีภาพที่แท้จริง เริ่มจากการที่คุณ มีสิทธิในทรัพย์สินของตัวเอง . อาจารย์พิริยะพูดในรายการ BitcoinTalk EP 205 ว่า
“ในพุทธศาสนาเนี่ย พูดถึงเรื่องของการไม่ยึดติด แต่การไม่ยึดติด ไม่ได้แปลว่า การบังคับให้คนทุกคนนั้นเนี่ย ไม่สามารถมีอะไรเป็นของตัวเองได้เลย คนละเรื่องกัน...มันคือ ชีวิตที่ดีไซน์โดยภาครัฐ...มันคือระบบ Socialism, Communism นะฮะ…”
ฟังแค่นี้ก็เห็นภาพเลยว่า...ความว่างเปล่า การไม่ยึดติด แบบที่พุทธพูดถึง กับความ “ไม่มี” แบบที่ระบบจัดสรรให้ มันคนละเรื่องกันเลย
แบบแรก คุณเลือกวาง เพราะคุณมีเสรีภาพในการตัดสินใจเอง แบบหลัง คุณถูกบังคับให้วาง เพราะคุณไม่มีสิทธิแม้แต่จะเลือกถือ . ถ้าคุณไม่มีสิทธิในทรัพย์สินของคุณเอง แล้วคุณจะมีสิทธิในอะไรได้อีกในชีวิต แต่ถ้าแนวคิด You will own nothing เป็นจริง เรากำลังพูดถึงสังคมที่ทุกสิ่งเป็นของรัฐ ในขณะที่คุณทำได้แค่เช่าใช้ชีวิตของตัวเองเท่านั้น . เอาแค่เงินสดที่คุณถืออยู่… เงินที่รัฐประกาศให้เป็นเงินถูกกฎหมาย มันเป็นของเราจริงหรือเปล่านะ ในเมื่อรัฐสามารถทำให้มันเฟ้อ และเสื่อมค่าลงได้ตลอดเวลา เท่านั้นยังไม่พอ ถ้าวันหนึ่งรัฐยึดมันไป ปิดบัญชีหรืออายัดเงินของคุณทั้งหมด คุณจะปกป้องสิทธิของตัวเองได้อย่างไร
มีเพียงทรัพย์สินชนิดเดียวในโลก ที่ไม่สามารถถูกยึดได้ด้วยอำนาจรัฐ และได้กลายเป็นสัญลักษณ์ของการพึ่งพาตนเอง ทั้งทางเศรษฐกิจ และเสรีภาพส่วนบุคคล นั่นก็คือ บิตคอยน์ . ลองถามตัวเองดูครับ ว่า...คุณอยากไม่มีอะไร เพราะคุณเลือกที่จะวางเอง หรือคุณไม่มีอะไรให้วาง เพราะเขาไม่ให้คุณมีตั้งแต่แรก
สองอย่างนี้...ดูคล้ายกันมากนะครับ แต่ในใจคนที่วาง มันต่างกันคนละโลก ระหว่างวาง...เพราะเข้าใจ กับวาง...เพราะไม่มีสิทธิถือมันตั้งแต่แรก
ถ้าคุณอ่านมาถึงตรงนี้ ผมคิดว่า คุณน่าจะเห็นเหมือนกันว่า...
เสรีภาพในการเลือกถือหรือเลือกวาง คือหัวใจของทั้งพุทธ และ Libertarianism 🙃
และถ้าคุณเชื่อในการเป็นอิสรชน อย่าลืมปกป้องสิทธิของตน เพราะเราทุกคน...ควรมีเสรีภาพในการตัดสินใจ และรับผลของการตัดสินใจนั้นด้วยตนเอง
Siamstr #Libertarianism
-
 @ 35da2266:15e70970
2025-04-16 03:43:02
@ 35da2266:15e70970
2025-04-16 03:43:02QdWVn542ZckzWEvFkyHenDWAI0kk58kbjgrYtvQBbbQXRXaxaRAlvjQ93NChwiNnfPaAEJ5R/hmuJ6FkTowumS9q0NP7uG6tA0RuTssdwNIORaN/wvqmz0GYme1Ci5RlNxtlHgeOyuPkLdiaolTt9CYlY2mV4gC1Tplkn7aP4mbXK+TJM9t6VsRR68GxShp8bLVK1qH3N6sPn9B7pkY2jEwi9GxGtZlf/jO3vS3lBgW79Ud2OYHbU3pauSdeM97+1TWvtMQt/iBlg54OB5Nb5pCTCNWDeJFD2wwavfQE8g9i91XBtt70z69shNrxLKHgpj6noC7QdUy1XZ49o3KSQw==?iv=B8YV090ont/MFRGbYBxpsA==
-
 @ 91266b9f:43dcba6c
2025-04-16 03:42:09
@ 91266b9f:43dcba6c
2025-04-16 03:42:09"No," I said, "you've got no right."
Sergeant Curtis sighed. "Come on, Mister Alton, I need you to work with me here."
"No," I said. "Absolutely not."
"He did it," shouted Mavis Harris, my recently new neighbor, leaning over the garden fence. "I saw him! He had a knife, a carving knife. And I heard the screaming and the shouting! He did it!"
"Thank you, Miss Harris," said Sergeant Curtis. "We've got it from here."
We were in my beautifully manicured backyard, sweating under the midday sun, along with six other police officers--all of them armed with shovels, ready to dig.
"This is an invasion of my privacy and I won't have it," I said.
"If you just tell us where your wife is we can get this all cleared up," he said.
"I'm not married," I said. "I've never been married."
Sergeant Curtis chewed on that for a bit, while he did the same to his bottom lip. "Girlfriend then. Partner?"
"I have no girlfriend. No partner. There's nobody at all," I said.
But there was. Sort of. Cindy, wonderful, difficult Cindy.
"He's lying!" said Mavis Harris. "I've seen her. Through the window. One time I called by when he wasn't here and she was just sitting in there, not moving. Wouldn't even answer the door. She must've been terrified, the poor girl. I bet he had her tied to the chair!"
That was absurd. Cindy wasn't into that kind of thing. I would never tie her to a chair and leave the house. That's crazy talk.
"We've got more than one eyewitness that says there's been a woman in the house with you," said Sergeant Curtis. "How about we get this woman on the phone, clear this up?"
"I can't make the impossible happen, Sergeant," I said, stiffly.
My back door opened and Constable Jenkins stepped onto the verandah. "Got a carving knife missing from a set of six," he said.
"I told you, he went after her with a knife!" said Mavis Harris.
She was right. Things had got heated. Words were said. The knife had made an appearance. There had definitely been some stabby-cutty action. Much to my dismay. I hated that it happened. I guess I was going to have to live with the damage.
Sergeant Curtis sighed. "This isn't looking good, Mr Alton."
"I bet he put her under the roses!" said Mavis Harris. "That's where I saw him heading with the body!"
"Alleged body," I muttered.
"Jenkins, any sign of blood in there?" said Sergeant Curtis.
"None whatsoever," said Jenkins. "Not even under black light. Couldn't spot any in the garden either."
"He must have cleaned it up," said Mavis. "Bleach. Bleach will clean up anything. And I saw him, I saw him carry her out and she had what looked like a knife sticking out of her chest!"
"Last chance, Mr Alton," said Curtis, "let's get this lady friend of yours on the phone and clear this up."
"I told you, I can't do the impossible," I said.
"Then you're leaving me no choice," he said.
He turned and nodded at the waiting officers with their shovels. "Start with the rose garden," he said.
They rolled up their sleeves with obvious relish and got to work.
"This is destruction of private property," I said. "When you're done, every rose petal, every grain of soil, better be back exactly as it was. Or you'll be dealing with my lawyer."
"Don't worry," said Sergeant Curtis, "I assure you everything will be put back as we found it. Whether we uncover anything or not."
As we watched the officers desecrate my rose garden, Sergeant Curtis said, "You know there's probably a few million square kilometers of country, forests, lakes, beaches, and do you know where most killers bury their wives or husbands? On their own property, right in their own backyard."
"Convenience trumps everything, I suppose," I said.
"Laziness," said Sergeant Curtis, "most casual criminals are just bone lazy."
"Or," I said, "they maybe wanted to keep their loved ones close."
Sergeant Curtis looked at me, eyes narrowed. "Is that what it is? You kill them, but somehow you want to keep them close?"
I shrugged. "Things happen. But you still love them. Maybe, you want them to be close to home," I said.
Curtis glared at me.
After a while Constable Jenkins climbed out of the rose garden and moped his sweating forehead with his sleeve. "Nothing here," he said. "This soil is pretty solid, hasn't been dug up in a while."
"The other rose bed," said Mavis Harris, "he must have used the other rose bed, beside the shed."
Damn that woman, why won't she keep her mouth shut?!
Constable Jenkins went over and stabbed his shovel into the dirt a few times. "Yeah," he said, "this has been dug up recently."
"Okay," said Sergeant Curtis, "get to it."
"I really must protest," I said. "This is a violation of my rights!"
"I'm sure we'll be done soon enough," said Sergeant Curtis, with a tight smile.
I turned and stared daggers at Mavis Harris, who haughtily thrust her nose and chin in the air, a smug smile on her face. Damn that woman and her meddling ways!
The officers found my second rose garden easier going. They were at it about twenty minutes when Constable Jenkins suddenly said, "Jesus Christ!"
"What, what is it?" said Sergeant Curtis, coming to attention.
"I ... I don't know," said Jenkins. "Hang on ..." He scraped at the dirt and then leaned over, grabbed something and lifted it out of the dirt.
A leg.
"Jeezuz," said Jenkins, letting the leg drop back into the soil. "I think we found her!"
"I knew it," said Mavis Harris. "I told you! Didn't I tell you? He did it! He killed her!"
They worked quickly now, gently digging and scraping away dirt until they could lift her other leg out. My beautiful Cindy doll.
"We've got a knife," said Jenkins, "but it's ... it's ..."
He turned to look at me, his face twisted in disgust.
"What is it?" said Curtis.
Jenkins swallowed, hard. "It's ... the knife, it's ... it's stabbed ... up between her legs, if, uh, if you know what I mean."
"Oh my god, you absolute monster," said Mavis Harris, clutching the neck of her blouse.
I sighed. They had no right. No right. This was a private matter. It was nobody's business but mine and Cindy's. We would work it out, Cindy and me. We always did.
"Okay," said Curtis, "get her out of there, quick! Check for a pulse, just in case."
"She's gone, Sarge," said Jenkins. "She's stone cold dea--wait, hang on a second."
He did some more digging and scraping with the shovel and slowly eased my Cindy all the way out of the dirt.
"Oh, bloody hell " said Jenkins. "You have got to be kidding."
"What, what is it?" said Curtis.
"Oh my, oh my Lord," said Mavis Harris, "I feel sick."
Jenkins struggled a bit with the weight, but managed to get Cindy upright. She is a bit of a heavy lass, I have to admit.
"It's a doll," said Jenkins. "It's just a doll, a sex doll, I think." He lifted Cindy's arm and made her give a little wave. "Seems to be silicon. Wow, very life-like, I must say." He was gently squeezing Cindy's arm and nose and cheek with his fingertips.
I seethed. The disrespect!
"A doll?" said Curtis.
"Yes, sir."
Curtis turned to me, his face a throttled purple colour. "A bloody sex doll?!"
I said nothing.
He struggled to keep his anger in check. "I could arrest you for obstruction of justice, Alton, for wasting Police time and resources," he said.
"How?" I said. "I was nothing but absolutely honest with you. There was no wife, no girlfriend, no body. I told you this repeatedly. You chose to ignore me and you, sir, have wasted not only my time, but that of your department and your own men."
I left him there, chewing air, and went to Jenkins and took Cindy gently in my arms. Her wounds were bad but not unamendable.
"Pervert," hissed Mavis Harris. "He's a dirty little pervert!"
I headed for the house, but paused at the back door and said, "I will expect you to return my rose gardens to their absolute pristine condition. My lawyer already doesn't like your department, not one bit, Sergeant Curtis."
I did not wait for a reply. I went inside and closed the door, quietly, behind me.
Night was coming on and the police had returned my garden to its former glory, and departed. A cool breeze drifted through the kitchen window.
I was at the table with Cindy, tending her wounds. Silicon glue isn't cheap, I'll tell you that, and it would leave Cindy with some scars, unfortunately. If I'm honest, I don't think she was all that pleased about it. As I knelt down to treat a wound across her ribcage, I copped her knee right in my groin.
"Ugh!" I said, the wind snapping out of me and tears rimming my eyes.
I reached out to steady myself and that's when she lurched forward, out of her chair, and headbutted me square in the face.
"For godsakes, Cindy!" I said.
She was baring down on me. I grabbed her by the shoulders, pushing her up and back, but like I said, she wasn't exactly a lightweight. I staggered back with her falling into me, and I winced as the edge of the kitchen counter stabbed into the small my back. Cindy gave me another hit to the testicles with her hand, making me gasp.
I rolled us around, putting her back against counter, silicon squeaking against marble--see how she likes it. I almost took another groin hit from her other hand. I was bending her back over the kitchen sink and without realising it, I had grabbed one of the serrated steak knives in my fist, raised it over my head, and was ready to drive it down into the open O of her mouth.
And that's when I looked past Cindy's head, out the kitchen window, across the fence, and over there in her kitchen window was Mavis Harris. Staring right at me, at us, her mouth an identical open O to Cindy's.
We stared at each other for a long moment, and then I reached up and slowly closed the kitchen blinds.
I sighed. I decided that Mavis Harris was a problem I just couldn't tolerate. Her constant invasion of my privacy was one thing, but calling the police was unacceptable. I would have to take care of her at my earliest opportunity. But carefully. And I had just the spot for her, out behind her very own shed.
Right next to Henry Patterson, the last neighbour and resident of that house, who had also gotten far too nosey for his own good.
Yes, a real nice spot, and close to home.
-
 @ c066aac5:6a41a034
2025-04-15 22:06:06
@ c066aac5:6a41a034
2025-04-15 22:06:06-Interpretive ~~loops~~ Technology Poetry by Zachariah Sanders
I am testing ~~the loops~~Comet.
It fit many loop It has many features.~~There are loops~~ There are cool tools.
I mean, like, really cool;
I'm going to embed ~~the loops~~ a video that lives rent free in my mind:
https://www.youtube.com/watch?v=peXNAwzyJas
Anyway, long live innovation!
~~Long live the loops~~
https://github.com/nodetec/comet
loops #comet #article #nostrinnovation #nostr #willzap4loops
-
 @ 35da2266:15e70970
2025-04-16 03:38:20
@ 35da2266:15e70970
2025-04-16 03:38:209Jqq62GzpfwYvFgcKiQX5Fy6yyD5qIVdZ2hVOr79wFf7vtXyELuBT6RXik9TDnsf4CSqQQwbTbJ/8zO2hm/H0iEvBJj2fGGf/lJQ9OYtL56bIGbdPWDiFO0cG/aWaLEX+i5kc9aaxXvlYtdQVakkpcIo4FS4u+Opi7NmGJtLYkixj9njZ6RXnRhjYtBDqS/I+lsPM+8QlLxgUJyzX2FSWhMNCEkwGQyY7WL5ve3HmUyOHgvnE0jD5POQc8K576ujKv/7bIgVsLHDjM4YzGUnVozy5JFNIsuAFUU5aBXsqABeiAwTDBMpid+3kvT3THISm2YM2KSWz12RTI8yb5NduQ==?iv=qQok9QsgRXAZajfYeiFqSA==
-
 @ 9223d2fa:b57e3de7
2025-04-15 02:54:00
@ 9223d2fa:b57e3de7
2025-04-15 02:54:0012,600 steps
-
 @ 35da2266:15e70970
2025-04-16 03:36:00
@ 35da2266:15e70970
2025-04-16 03:36:00lTFfszFRc574FKS4B4a6nuGhDb75H+3br1OH+YeiocHc3ef4q7oFvPns983W0dA911/8OMRW/+UFE7EESUeHCk0YQ6KSqzbzNAU3MKJaw8mwRmAzgyizq+3lTU0lB+A/CdbTmfmJP9eiyPsN/hkyPaYm+w35nhzEzFYeXfS6GZkB/vDoeyQVK8pwaLXjeo6Xo2qhZGu0V9DJEMHZjfmnCvXc1OR/JDOCz45pNmPR4SRBrsckZLNbmS9FGWQY9ffiSkA6YvuioiEqV5jmVz68F08zt57nm8BMnlQDdtI/TDZ8/kmXyBgcBwOM0ep5nTod7jEu+ydFNu/RHfZdWNetGQ==?iv=PEfCBpzguAgauYj3mhiO4Q==
-
 @ e1b184d1:ac66229b
2025-04-15 20:09:27
@ e1b184d1:ac66229b
2025-04-15 20:09:27Bitcoin is more than just a digital currency. It’s a technological revolution built on a unique set of properties that distinguish it from all other financial systems—past and present. From its decentralized architecture to its digitally verifiable scarcity, Bitcoin represents a fundamental shift in how we store and transfer value.
1. A Truly Decentralized Network
As of April 2025, the Bitcoin network comprises approximately 62,558 reachable nodes globally. The United States leads with 13,791 nodes (29%), followed by Germany with 6,418 nodes (13.5%), and Canada with 2,580 nodes (5.43%). bitnodes
This distributed structure is central to Bitcoin’s strength. No single entity can control the network, making it robust against censorship, regulation, or centralized failure.

2. Open Participation at Low Cost
Bitcoin's design allows almost anyone to participate meaningfully in the network. Thanks to its small block size and streamlined protocol, running a full node is technically and financially accessible. Even a Raspberry Pi or a basic PC is sufficient to synchronize and validate the blockchain.
However, any significant increase in block size could jeopardize this accessibility. More storage and bandwidth requirements would shift participation toward centralized data centers and cloud infrastructure—threatening Bitcoin’s decentralized ethos. This is why the community continues to fiercely debate such protocol changes.
3. Decentralized Governance
Bitcoin has no CEO, board, or headquarters. Its governance model is decentralized, relying on consensus among various stakeholders, including miners, developers, node operators, and increasingly, institutional participants.
Miners signal support for changes by choosing which version of the Bitcoin software to run when mining new blocks. However, full node operators ultimately enforce the network’s rules by validating blocks and transactions. If miners adopt a change that is not accepted by the majority of full nodes, that change will be rejected and the blocks considered invalid—effectively vetoing the proposal.
This "dual-power structure" ensures that changes to the network only happen through widespread consensus—a system that has proven resilient to internal disagreements and external pressures.
4. Resilient by Design
Bitcoin's decentralized nature gives it a level of geopolitical and technical resilience unmatched by any traditional financial system. A notable case is the 2021 mining ban in China. While initially disruptive, the network quickly recovered as miners relocated, ultimately improving decentralization.
This event underlined Bitcoin's ability to withstand regulatory attacks and misinformation (FUD—Fear, Uncertainty, Doubt), cementing its credibility as a global, censorship-resistant network.
5. Self-Sovereign Communication
Bitcoin enables peer-to-peer transactions across borders without intermediaries. There’s no bank, payment processor, or centralized authority required. This feature is not only technically efficient but also politically profound—it empowers individuals globally to transact freely and securely.
6. Absolute Scarcity
Bitcoin is the first asset in history with a mathematically verifiable, fixed supply: 21 million coins. This cap is hard-coded into its protocol and enforced by every full node. At the atomic level, Bitcoin is measured in satoshis (sats), with a total cap of approximately 2.1 quadrillion sats.
This transparency contrasts with assets like gold, whose total supply is estimated and potentially (through third parties on paper) expandable. Moreover, unlike fiat currencies, which can be inflated through central bank policy, Bitcoin is immune to such manipulation. This makes it a powerful hedge against monetary debasement.
7. Anchored in Energy and Time
Bitcoin's security relies on proof-of-work, a consensus algorithm that requires real-world energy and computation. This “work” ensures that network participants must invest time and electricity to mine new blocks.
This process incentivizes continual improvement in hardware and energy sourcing—helping decentralize mining geographically and economically. In contrast, alternative systems like proof-of-stake tend to favor wealth concentration by design, as influence is determined by how many tokens a participant holds.

8. Censorship-Resistant
The Bitcoin network itself is inherently censorship-resistant. As a decentralized system, Bitcoin transactions consist of mere text and numerical data, making it impossible to censor the underlying protocol.
However, centralized exchanges and trading platforms can be subject to censorship through regional regulations or government pressure, potentially limiting access to Bitcoin.
Decentralized exchanges and peer-to-peer marketplaces offer alternative solutions, enabling users to buy and sell Bitcoins without relying on intermediaries that can be censored or shut down.
9. High Security
The Bitcoin blockchain is secured through a decentralized network of thousands of nodes worldwide, which constantly verify its integrity, making it highly resistant to hacking. To add a new block of bundled transactions, miners compete to solve complex mathematical problems generated by Bitcoin's cryptography. Once a miner solves the problem, the proposed block is broadcast to the network, where each node verifies its validity. Consensus is achieved when a majority of nodes agree on the block's validity, at which point the Bitcoin blockchain is updated accordingly, ensuring the network's decentralized and trustless nature.
Manipulation of the Bitcoin network is virtually impossible due to its decentralized and robust architecture. The blockchain's chronological and immutable design prevents the deletion or alteration of previously validated blocks, ensuring the integrity of the network.
To successfully attack the Bitcoin network, an individual or organization would need to control a majority of the network's computing power, also known as a 51% attack. However, the sheer size of the Bitcoin network and the competitive nature of the proof-of-work consensus mechanism make it extremely difficult to acquire and sustain the necessary computational power. Even if an attacker were to achieve this, they could potentially execute double spends and censor transactions. Nevertheless, the transparent nature of the blockchain would quickly reveal the attack, allowing the Bitcoin network to respond and neutralize it. By invalidating the first block of the malicious chain, all subsequent blocks would also become invalid, rendering the attack futile and resulting in significant financial losses for the attacker.
One potential source of uncertainty arises from changes to the Bitcoin code made by developers. While developers can modify the software, they cannot unilaterally enforce changes to the Bitcoin protocol, as all users have the freedom to choose which version they consider valid. Attempts to alter Bitcoin's fundamental principles have historically resulted in hard forks, which have ultimately had negligible impact (e.g., BSV, BCH). The Bitcoin community has consistently rejected new ideas that compromise decentralization in favor of scalability, refusing to adopt the resulting blockchains as the legitimate version. This decentralized governance model ensures that changes to the protocol are subject to broad consensus, protecting the integrity and trustworthiness of the Bitcoin network.
Another source of uncertainty in the future could be quantum computers. The topic is slowly gaining momentum in the community and is being discussed.
Your opinion
My attempt to write an article with Yakyhonne. Simple editor with the most necessary formatting. Technically it worked quite well so far.
Some properties are listed in the article. Which properties are missing and what are these properties?
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ 7d33ba57:1b82db35
2025-04-15 19:33:07
@ 7d33ba57:1b82db35
2025-04-15 19:33:07Nestled in the lush Our Valley in northern Luxembourg, Vianden is a charming riverside town known for its stunning medieval castle, cobbled streets, and peaceful atmosphere. Surrounded by forested hills and steeped in history, it’s the perfect day trip—or even a peaceful overnight getaway—from Luxembourg City.
🏰 Top Highlight: Vianden Castle
- One of Europe’s most beautiful feudal castles, perched dramatically on a hilltop
- Built between the 11th and 14th centuries, with Romanesque and Gothic elements
- Lovingly restored, it now features furnished rooms, exhibitions, and epic valley views
- Visit in autumn or winter for a real storybook vibe, or during medieval festivals in summer for a lively twist
🌿 Things to Do in Vianden
1️⃣ Wander the Old Town
- Stroll the cobbled lanes, cross stone bridges, and admire the pastel-colored houses along the river
- Stop at a café by the water and just soak in the Alpine-style charm
2️⃣ Take the Chairlift
- Ride Luxembourg’s only chairlift up the hill above Vianden
- Amazing panoramic views of the town, river, and surrounding forests
- You can hike back down through wooded trails—it’s magical in the fall
3️⃣ Victor Hugo House
- Famous French writer Victor Hugo lived in exile here in the 1870s
- His former home is now a museum with personal items, manuscripts, and 19th-century decor
4️⃣ Hiking & Nature
- Vianden is surrounded by forested trails and river paths, perfect for hiking and biking
- You can follow the Our Valley Trail or parts of the Escapardenne trail toward the Belgian border
🍽️ Local Flavors
- Try hearty Luxembourgish dishes like Judd mat Gaardebounen (smoked pork neck with broad beans)
- Enjoy fresh trout from local rivers, Luxembourgish wine, or a slice of Apfelkuchen with coffee
- The town’s cozy inns and traditional restaurants make dining here feel warm and personal
🚆 Getting There
- From Luxembourg City: About 1.5 hours by public transport (train + bus combo) or 45 minutes by car
- Bonus: Public transport is free in Luxembourg!
-
 @ 39cc53c9:27168656
2025-04-09 07:59:35
@ 39cc53c9:27168656
2025-04-09 07:59:35The new website is finally live! I put in a lot of hard work over the past months on it. I'm proud to say that it's out now and it looks pretty cool, at least to me!
Why rewrite it all?
The old kycnot.me site was built using Python with Flask about two years ago. Since then, I've gained a lot more experience with Golang and coding in general. Trying to update that old codebase, which had a lot of design flaws, would have been a bad idea. It would have been like building on an unstable foundation.
That's why I made the decision to rewrite the entire application. Initially, I chose to use SvelteKit with JavaScript. I did manage to create a stable site that looked similar to the new one, but it required Jav aScript to work. As I kept coding, I started feeling like I was repeating "the Python mistake". I was writing the app in a language I wasn't very familiar with (just like when I was learning Python at that mom ent), and I wasn't happy with the code. It felt like spaghetti code all the time.
So, I made a complete U-turn and started over, this time using Golang. While I'm not as proficient in Golang as I am in Python now, I find it to be a very enjoyable language to code with. Most aof my recent pr ojects have been written in Golang, and I'm getting the hang of it. I tried to make the best decisions I could and structure the code as well as possible. Of course, there's still room for improvement, which I'll address in future updates.
Now I have a more maintainable website that can scale much better. It uses a real database instead of a JSON file like the old site, and I can add many more features. Since I chose to go with Golang, I mad e the "tradeoff" of not using JavaScript at all, so all the rendering load falls on the server. But I believe it's a tradeoff that's worth it.
What's new
- UI/UX - I've designed a new logo and color palette for kycnot.me. I think it looks pretty cool and cypherpunk. I am not a graphic designer, but I think I did a decent work and I put a lot of thinking on it to make it pleasant!
- Point system - The new point system provides more detailed information about the listings, and can be expanded to cover additional features across all services. Anyone can request a new point!
- ToS Scrapper: I've implemented a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. This is still in development and it will improve for sure, but it works pretty fine right now!
- Search bar - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. Looking for VPN services? Just search for "vpn"!
- Transparency - To be more transparent, all discussions about services now take place publicly on GitLab. I won't be answering any e-mails (an auto-reply will prompt to write to the corresponding Gitlab issue). This ensures that all service-related matters are publicly accessible and recorded. Additionally, there's a real-time audits page that displays database changes.
- Listing Requests - I have upgraded the request system. The new form allows you to directly request services or points without any extra steps. In the future, I plan to enable requests for specific changes to parts of the website.
- Lightweight and fast - The new site is lighter and faster than its predecessor!
- Tor and I2P - At last! kycnot.me is now officially on Tor and I2P!
How?
This rewrite has been a labor of love, in the end, I've been working on this for more than 3 months now. I don't have a team, so I work by myself on my free time, but I find great joy in helping people on their private journey with cryptocurrencies. Making it easier for individuals to use cryptocurrencies without KYC is a goal I am proud of!
If you appreciate my work, you can support me through the methods listed here. Alternatively, feel free to send me an email with a kind message!
Technical details
All the code is written in Golang, the website makes use of the chi router for the routing part. I also make use of BigCache for caching database requests. There is 0 JavaScript, so all the rendering load falls on the server, this means it needed to be efficient enough to not drawn with a few users since the old site was reporting about 2M requests per month on average (note that this are not unique users).
The database is running with mariadb, using gorm as the ORM. This is more than enough for this project. I started working with an
sqlitedatabase, but I ended up migrating to mariadb since it works better with JSON.The scraper is using chromedp combined with a series of keywords, regex and other logic. It runs every 24h and scraps all the services. You can find the scraper code here.
The frontend is written using Golang Templates for the HTML, and TailwindCSS plus DaisyUI for the CSS classes framework. I also use some plain CSS, but it's minimal.
The requests forms is the only part of the project that requires JavaScript to be enabled. It is needed for parsing some from fields that are a bit complex and for the "captcha", which is a simple Proof of Work that runs on your browser, destinated to avoid spam. For this, I use mCaptcha.
-
 @ e968e50b:db2a803a
2025-04-15 17:45:27
@ e968e50b:db2a803a
2025-04-15 17:45:27Hey cinephiles, I'm just crossposting this bounty that remains unclaimed from last week. It occurred to me that you may be a more receptive audience to this game that I made than the folks monitoring the gamers territory. Either way, let me know what you think. I've been told it's too hard...but maybe not for you!
https://stacker.news/items/937363
originally posted at https://stacker.news/items/944303
-
 @ e0921d61:e0fe7bd5
2025-04-15 16:13:32
@ e0921d61:e0fe7bd5
2025-04-15 16:13:32Hans-Hermann Hoppe explains the capitalist process as driven by time preference, how people value present vs. future goods. Economic growth hinges on savings and investment, and this shapes our prosperity.
Factors like population, natural resources, and technology matter, but Hoppe argues they're secondary. Without prior savings and investment, even the richest resources and best technology remain untapped.
True economic advancement happens through increasing per capita invested capital, raising productivity, real incomes, and further lowering time preferences. This creates a self-reinforcing cycle of prosperity.
Hoppe claims this process naturally continues smoothly until scarcity itself disappears, unless people voluntarily choose leisure over more wealth. This growth has no inherent reason to halt abruptly.
This smooth capitalist cycle, however, is disrupted when government enters the picture. Government control of resources it didn’t earn or acquire legitimately distorts incentives and investment.
Government monopolization of money through fractional reserve banking artificially lowers interest rates.
Entrepreneurs mistakenly think, and are incentivized to think, there's more savings, so more unsustainable investments proliferate.
Without real savings backing these projects, a painful correction (a bust following the boom) inevitably occurs.
Investments must eventually realign with actual savings, thus leading to bankruptcies and unemployment.
Hoppe concludes that boom-bust cycles aren’t natural. They’re directly caused by government-created credit expansion. Unless governments stop manipulating fiat money supply, these cycles remain unavoidable.
-
 @ 75869cfa:76819987
2025-04-15 16:12:57
@ 75869cfa:76819987
2025-04-15 16:12:57GM, Nostriches!
The Nostr Review is a biweekly newsletter focused on Nostr statistics, protocol updates, exciting programs, the long-form content ecosystem, and key events happening in the Nostr-verse. If you’re interested, join me in covering updates from the Nostr ecosystem!
Quick review:
In the past two weeks, Nostr statistics indicate over 212,000 daily trusted pubkey events. The number of new users has seen a notable increase, with profiles with contact lists three times higher than the previous period. More than 9 million events have been published, reflecting a 3% decrease. Total Zap activity stands at approximately 19 million, marking a 8.7% increase.
Additionally, 14 pull requests were submitted to the Nostr protocol, with 4 merged. A total of 45 Nostr projects were tracked, with 7 releasing product updates, and over 359 long-form articles were published, 21% focusing on Bitcoin and Nostr. During this period, 5 notable events took place, and 2 significant events are upcoming.
Nostr Statistics
Based on user activity, the total daily trusted pubkeys writing events is about 212,000, representing a slight 4 % decrease compared to the previous period. Daily activity peaked at 17053 events, with a low of approximately 14674.
The number of new users has increased significantly. Profiles with contact lists are now around 82,248, which is three times higher than the previous period. The number of pubkeys writing events has also increased by 20% compared to the last period.
The total number of note events published is around 9 million, reflecting a 3% decrease. Posts remain the most dominant in terms of volume, totaling approximately 1.8 million, which is a 7.3 % increase. Reposts have decreased by about 9%.
For zap activity, the total zap amount is about 19 million, showing an decrease of over 8.7% compared to the previous period.
Data source: https://stats.nostr.band/
NIPs
fix(nip-57): update relays tag in Appendix D to "MUST" for consistency (#1858) #1867
rajanarahul93 updates the relays tag in Appendix D of nips/57.md from "SHOULD" to "MUST" for consistency with the rest of the document and the intended specification behavior.The change ensures that the specification aligns with the strict expectations described in the main body of NIP-57. It avoids confusion for implementers and enforces consistency across clients.
Add guidelines tag to NIP-29 group metadata #1873
nostr:npub16zsllwrkrwt5emz2805vhjewj6nsjrw0ge0latyrn2jv5gxf5k0q5l92l7 adds another tag to the group metadata to include community guidelines or rules for participating in the group. The research has shown that communicating social norms is an essential component of a healthy community, so it deserves to be included as an example in the NIP here, not as a required tag necessarily, but as a standard field that we hope will be adopted by other NIP-29 clients.
Add Diff and Permalink kinds #1875
nostr:npub1ehhfg09mr8z34wz85ek46a6rww4f7c7jsujxhdvmpqnl5hnrwsqq2szjqv is proposing a NIP that introduces two new kinds of git events, intended to be drop-in replacements for GitHub permalinks and diff links respectively. The purpose of these kinds is to enable conversations and comments about specific lines of code, either in a given commit or the diff of two commits. These kinds are distinct from the code snippet introduced in NIP-C0 as the content of the events are not intended to be executable rather to directly reference code or documentation in a Git repo precisely and immutably.
Notable Projects
Primal nostr:npub12vkcxr0luzwp8e673v29eqjhrr7p9vqq8asav85swaepclllj09sylpugg
The update is now live on the App Store,the version 2.1.49 is bringing several improvements and fixes: * Support for animated GIF uploads * Resolved issues with zap.stream URLs * Improved deep linking to threads * Fixed rendering of mentioned events with unknown kinds
YakiHonne nostr:npub1yzvxlwp7wawed5vgefwfmugvumtp8c8t0etk3g8sky4n0ndvyxesnxrf8q
- Redefine social & on-chain consumption with seamless payments, voting, and gaming — all within your feed.
- Build Mini Apps easily with 3 creation modes & reach 170+ countries . YakiHonne's payment infrastructure empowers Mini Apps with efficient support, lowering costs & barriers to drive growth.
Gossip Release 0.14.af nostr:npub189j8y280mhezlp98ecmdzydn0r8970g4hpqpx3u9tcztynywfczqqr3tg8
- Simple relay list. Gossip will just use your relays. No more connecting to strange relays or other outbox model nonsense.
- Terminal UI: ditched egui because it is too complex and presents a security risk.
- Supporting industry standard VT-102 terminal escape sequences. Just fire up your favorite VT-100 or VT-102 terminal and enjoy the ncurses magic.
- Bringing back blinking text!
- Lowercasing: automatically lowercases ODELL's posts
- Extended hellthreads: Auto-tag everybody on nostr, and also everybody on X, Mastodon and BlueSky.
- Language choice: For those of you who don't like the rust language, we are releasing it in golang. We intend to release a new language every month. Next month: brainfuck.
- Impersonation: You know you can login to gossip with somebody else's npub to see
- And more.
Nostur nostr:npub1n0stur7q092gyverzc2wfc00e8egkrdnnqq3alhv7p072u89m5es5mk6h0
- Removed GIF button
Alby nostr:npub1getal6ykt05fsz5nqu4uld09nfj3y3qxmv8crys4aeut53unfvlqr80nfm
They are releasing this alongside Alby Pro — a new subscription plan enhancing the experience for those who self-host Alby Hub * New Bitrefill— seamlessly buy giftcards directly in from your node * Sidebar and Settings page got a UI revamp * As always, added plenty of minor improvements and fixed some bug
Pokey v0.1.5 nostr:npub1h2685kkxa4q50qpexuae9geqep7frr0u8t8pcy9zj0xnza9phvtsnkd9tm
- Zap notifications now displays zapper's profile
- Pokey will skip notifications for events containing more than a configurable amount of tagged users (Hell Threads)
ZEUS v0.10.2 nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5
This release is centered around bug fixes. * Fixes an issue with LNURLs of fixed amounts * Fixes an issue in the currency converter where you were unable to re-add a currency you just removed * Fixes an issue where the payment path view would cause the app the crash * Fixes an issue where the standalone Point of Sale would be buggy if fiat rates weren't enabled * Fixes buggy behavior when creating a new Embedded LND wallet on Android * Fixes alignment issues with the Dropdown setting input * Fixes a bug on the Payment settings view where the slider threshold input would display incorrect units
Long-Form Content Eco
In the past two weeks, more than 359 long-form articles have been published, including over 54 articles on Bitcoin and more than 23 related to Nostr, accounting for 21% of the total content.
These articles about Nostr mainly explore its unique advantages over traditional social media platforms, particularly in decentralization, censorship resistance, and the flexibility of identity management. They also delve into the double-edged nature of anonymity, influence, and content moderation challenges within the Nostr ecosystem. On the technical side, updates such as NIP-19 support in Nostr-PHP and tools like the Blossom Uploader for enhanced media sharing are introduced. Some articles focus on practical guidance—like how to manage multiple Nostr profiles and wallets—while others emphasize creative and cultural aspects, calling for more bold, Nostr-native art. Additionally, there is ongoing exploration of Nostr’s potential in business applications and experimental features such as atomic signature swaps.
These articles about Bitcoin discuss a broad and continuously evolving ecosystem. They focus on major developments such as the upcoming Bitcoin halving event, the growing mainstream and institutional adoption driven by Bitcoin ETFs, and El Salvador’s bold “Bitcoin experiment,” questioning whether it is an economic breakthrough or a cautionary tale. The articles also delve into the mechanics of Bitcoin transaction fees, real-world experiences with the Lightning Network, and how DePIN enables individuals to turn everyday devices into income-generating tools—bringing decentralized living closer to reality.In addition, some articles revisit key historical moments in Bitcoin’s journey, such as the 2014 MIT giveaway of free Bitcoin and cultural milestones like the Bitcoin Film Festival, emphasizing the importance of storytelling in sustaining Bitcoin’s long-term vision.
Thank you, nostr:npub186a9aaqmyp436j0gkxl8yswhat2ampahxunpmfjv80qwyaglywhqswhd06, nostr:npub1uv0gf390d6592qmwyx3r232ehfvve0jamvg3jlpcjrg2qaam40qqk2dznr,
nostr:npub1dryseu6yv7evgz2f7pfzk6wht8flapcfv5l6r4y65pg5px293awqlwwfpc, nostr:npub1mgvwnpsqgrem7jfcwm7pdvdfz2h95mm04r23t8pau2uzxwsdnpgs0gpdjc, nostr:npub1nar4a3vv59qkzdlskcgxrctkw9f0ekjgqaxn8vd0y82f9kdve9rqwjcurn, nostr:npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm, nostr:npub186k25a5rymtae6q0dmsh4ksen04706eurfst8xc5uzjchwkxdljqe59hv0, nostr:npub1x7zk9nfqsjwuuwm5mpdu8eevsnu2kk0ff23fv58p45d50fhuvaeszg44p2, nostr:npub17eygccj7l9nmpnef042d09m37x33xvvmlkf4l5ur0fwt0jff9xws2guuk6, nostr:npub12ffylwm93rg03fekwl7nuncvalpqflf3pazeh3kywm3rmtjqyhwqhf3tsl, nostr:npub1fn4afafnasdqcm7hnxtn26s2ye3v3g2h2xave7tcce6s7zkra52sh7yg99, and others, for your work. Enriching Nostr’s long-form content ecosystem is crucial.Nostriches Global Meet Ups
Recently, several Nostr events have been hosted in different countries. * YakiHonne teamed up with nostr:npub1j580xmzqdvqp8rsv04m562kkvfj6yvp226m97yc88q72cxekucesamh4up, nostr:npub1tujexpy7s6qt4ecmptg6hsxemzpkjc6cg5739cqzttnjxv05efsshjllxq and La Bitcoineta to successfully host a series of Nostr Workshops. These events introduced the Nostr ecosystem and Bitcoin payments, giving attendees a hands-on opportunity to explore decentralized technologies through YakiHonne. Participants who registered and verified their accounts were eligible to claim exclusive rewards—and by inviting friends, they could unlock additional benefits and bonuses.
The Bitcoin Educators Unconference 2025 took place on April 10, 2025, at Bitcoin Park in Nashville, Tennessee, USA. This non-sponsored event followed an Unconference format, allowing all participants to apply as speakers and share their Bitcoin education experiences in a free and interactive environment. The event open-sourced all its blueprints and Standard Operating Procedures (SOPs) to encourage global communities to organize similar Unconference events around the world. * The Bitcoin Dada Innovation Summit* successfully concluded on April 12, 2025, at the Radisson Hotel (formerly Protea) in GRA-IKEJA, Lagos. The summit brought together Bitcoin innovators from across Africa and was filled with vibrant energy. Attendees engaged in insightful conversations with Bitcoin experts, connected with key opinion leaders and industry figures, participated in a practical wallet security masterclass, enjoyed exciting giveaways and surprises, and witnessed a memorable graduation ceremony.nostr:npub1tujexpy7s6qt4ecmptg6hsxemzpkjc6cg5739cqzttnjxv05efsshjllxq
Here is the upcoming Nostr event that you might want to check out. * The second BOBSpace Nostr Month Meetup will take place on Friday, April 25, 2025, at 6:30 PM in Bangkok. This special event features nostr:npub18k67rww6547vdf74225x4p6hfm4zvhs8t8w7hp75fcrj0au7mzxs30202m, the developer of Thailand’s home-grown Nostr client Wherostr, as the guest speaker. He will share his developer journey, the story behind building Wherostr, and how Nostr enables censorship-resistant communication. This is a Bitcoin-only meetup focused on the Nostr protocol and decentralized technologies. * Panama Blockchain Week 2025 will take place from April 22 to 24 at the Panama Convention Center in Panama City. As the first large-scale blockchain event in Central America, it aims to position Panama as a leading blockchain financial hub in Latin America. The event features a diverse lineup, including a blockchain conference, Investor’s Night, Web3 gaming experiences, tech exhibitions, and an after-party celebration.
Additionally, We warmly invite event organizers who have held recent activities to reach out to us so we can work together to promote the prosperity and development of the Nostr ecosystem.
Thanks for reading! If there’s anything I missed, feel free to reach out and help improve the completeness and accuracy of my coverage.
-
 @ 35da2266:15e70970
2025-04-16 02:44:06
@ 35da2266:15e70970
2025-04-16 02:44:06fG+OPtj+9qPneI6eoh8G6m0+aQfxG6wbyeRGwYYVUYyGgZrNCzT2srRaP2CYp+KtOYAazGaN9UfHhdrVZOePCEPFRT8g/g4NwKwf7DRK8bLKeG3CNXCt0dQ2I5I9hUd6/HytYhlTCm/aUBA6oG3PQ2+xHFiHdEtLnWAFDfHSNqbtIgvOGoxdTUxCfXtRlxk4epaV8CyGmyJ3PSttjCzChxvJiSoi8+W2LBZtwVqkuAu/Wn6iRv82ExyX47YtEDf6FsvDPDiM54GPkclOv/umdUGxCLSAAOUOlLfBKDLA2jaHzpv4bfiI/vzdSd/kzNkssxtY14X6f7C8qWmA6J3KxQ==?iv=tQfpmbUuub6Kw6Nx1/uRbw==
-
 @ 7d33ba57:1b82db35
2025-04-15 14:59:10
@ 7d33ba57:1b82db35
2025-04-15 14:59:10Tucked into a serene bay just 20 km south of Dubrovnik, Cavtat is a relaxed seaside town that mixes historic charm, clear Adriatic waters, pine-covered hills, and a welcoming small-town feel. It’s often seen as a peaceful alternative to Dubrovnik, with cobbled streets, pretty promenades, and hidden beaches**—perfect for those looking to unwind in style.
🌟 What to Do in Cavtat
1️⃣ Stroll the Seaside Promenade
- Palm-lined and picture-perfect, the Riva is the heart of Cavtat
- Lined with cafés, ice cream spots, and yachts bobbing in the harbor
- Great for a morning coffee or a golden hour walk
2️⃣ Explore the Old Town
- Compact and charming, full of red-roofed stone houses and quiet lanes
- Don’t miss the Rector’s Palace and Baroque St. Nicholas Church
3️⃣ Visit the Racic Mausoleum
- Designed by famed Croatian sculptor Ivan Meštrović
- Set on a hill with panoramic sea views and a peaceful atmosphere
4️⃣ Swim & Sunbathe
- Small coves, flat rocky spots, and crystal-clear turquoise waters
- Try Beach Kamen Mali or walk around the Rat Peninsula for secluded spots
- Great for snorkeling and paddleboarding
5️⃣ Take a Boat to Dubrovnik
- Water taxis run frequently—it's a stunning ride along the coast
- Spend the day exploring Dubrovnik’s Old Town, then return to Cavtat’s tranquility
🍽️ What to Eat
- Fresh seafood – grilled fish, calamari, or buzara (shellfish in white wine sauce)
- Peka – slow-cooked meat or octopus under an iron bell
- Local wines like Pošip (white) or Plavac Mali (red)
- Finish with rozata, a Dubrovnik-style custard dessert
🎯 Travel Tips
✅ Cavtat is 15 mins from Dubrovnik Airport, making it a perfect arrival or departure base
✅ Quieter than Dubrovnik—ideal for families, couples, or solo travelers
✅ Best time to visit: late spring to early fall
✅ Rent a bike or walk around the Rat Peninsula for nature and sea views -
 @ ba36d0f7:cd802cba
2025-04-06 16:43:05
@ ba36d0f7:cd802cba
2025-04-06 16:43:051. Reglas Esenciales
✔ Pieza Tocada, Pieza Movida: Si tocas una pieza, debes moverla (si es legal).
✔ Aviso de Jaque: Decir "jaque" al atacar al rey (opcional en torneos oficiales).
✔ Jaque Mate Termina: El juego acaba inmediatamente — no hay que capturar al rey.
✔ Oferta de Tablas: Puedes ofrecer tablas después de tu movimiento, antes de pulsar el reloj.
2. Etiqueta en Torneos
-
Saludo: Apretón de manos antes y después de la partida.
-
Silencio: No hablar durante el juego (excepto "jaque" o "¿tablas?").
-
Reloj: Presiónalo con la misma mano que movió.
-
Rendición: Voltea tu rey o di "me rindo" (no solo te vayas).
Errores Comunes
❌ Hacer ruido con las piezas para distraer.
❌ Mirar fijamente el tablero del rival.
❌ Hacer jugadas falsas para probar su atención.
3. Modales en Ajedrez Online
-
Sin Retrasos: Deja que el tiempo se agote solo si estás perdido.
-
Cortesía: Escribe "Buen juego" ("GG") al finalizar.
-
Evita el "Berserk": No abuses de configuraciones rápidas para presionar al rival.
Faltas Graves
❌ Trampas: Usar motores de análisis, mirar otras partidas.
❌ Spammear mensajes o emojis.
❌ Abandonar sin rendirse formalmente.
-
-
 @ 3ffac3a6:2d656657
2025-04-15 14:49:31
@ 3ffac3a6:2d656657
2025-04-15 14:49:31🏅 Como Criar um Badge Épico no Nostr com
nak+ badges.pageRequisitos:
- Ter o
nakinstalado (https://github.com/fiatjaf/nak) - Ter uma chave privada Nostr (
nsec...) - Acesso ao site https://badges.page
- Um relay ativo (ex:
wss://relay.primal.net)
🔧 Passo 1 — Criar o badge em badges.page
- Acesse o site https://badges.page
-
Clique em "New Badge" no canto superior direito
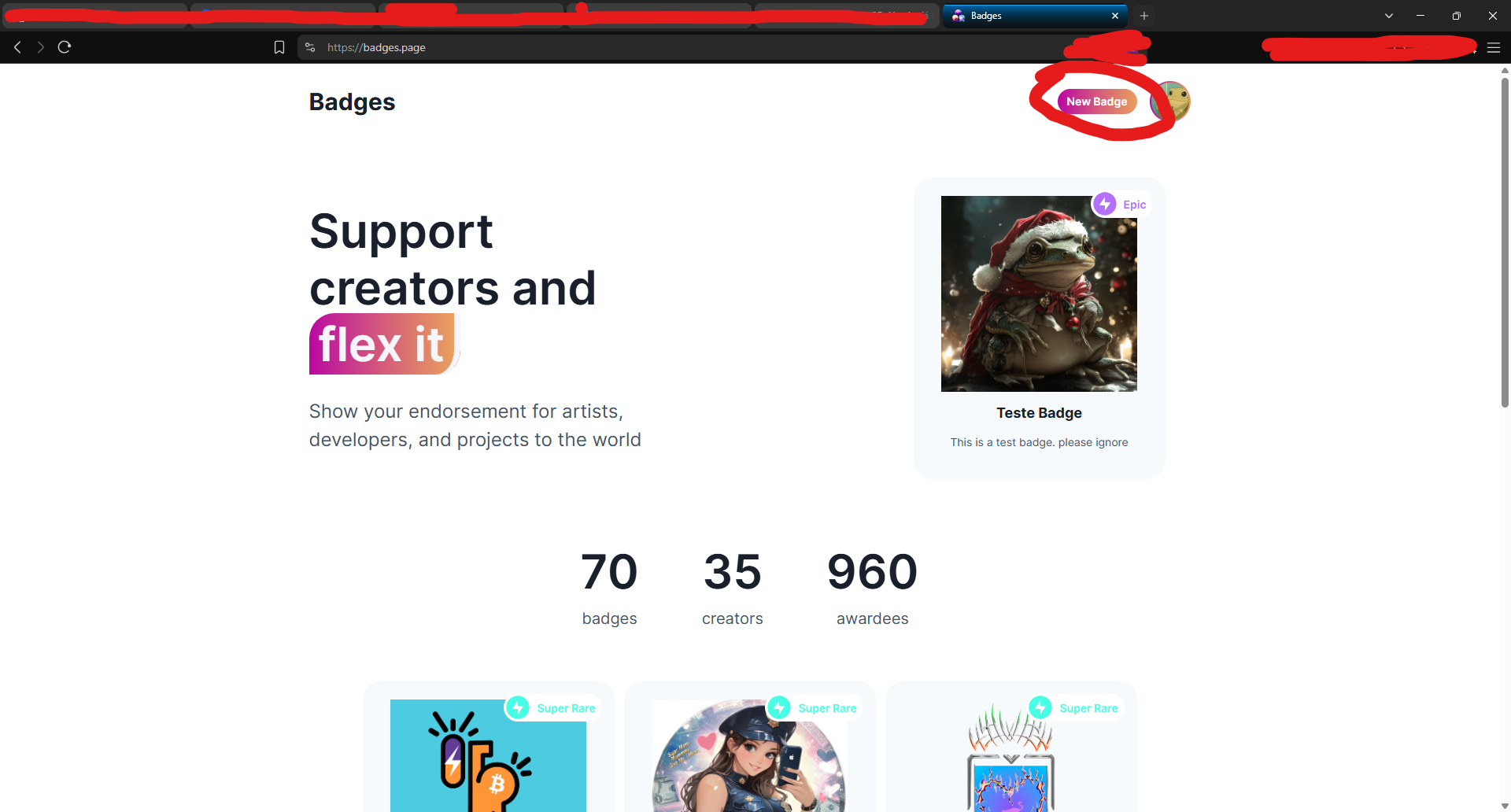
-
Preencha os campos:
- Nome (ex:
Teste Épico) - Descrição
-
Imagem e thumbnail
-
Após criar, você será redirecionado para a página do badge.
🔍 Passo 2 — Copiar o
naddrdo badgeNa barra de endereços, copie o identificador que aparece após
/a/— este é o naddr do seu badge.Exemplo:
nostr:naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Copie:
naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0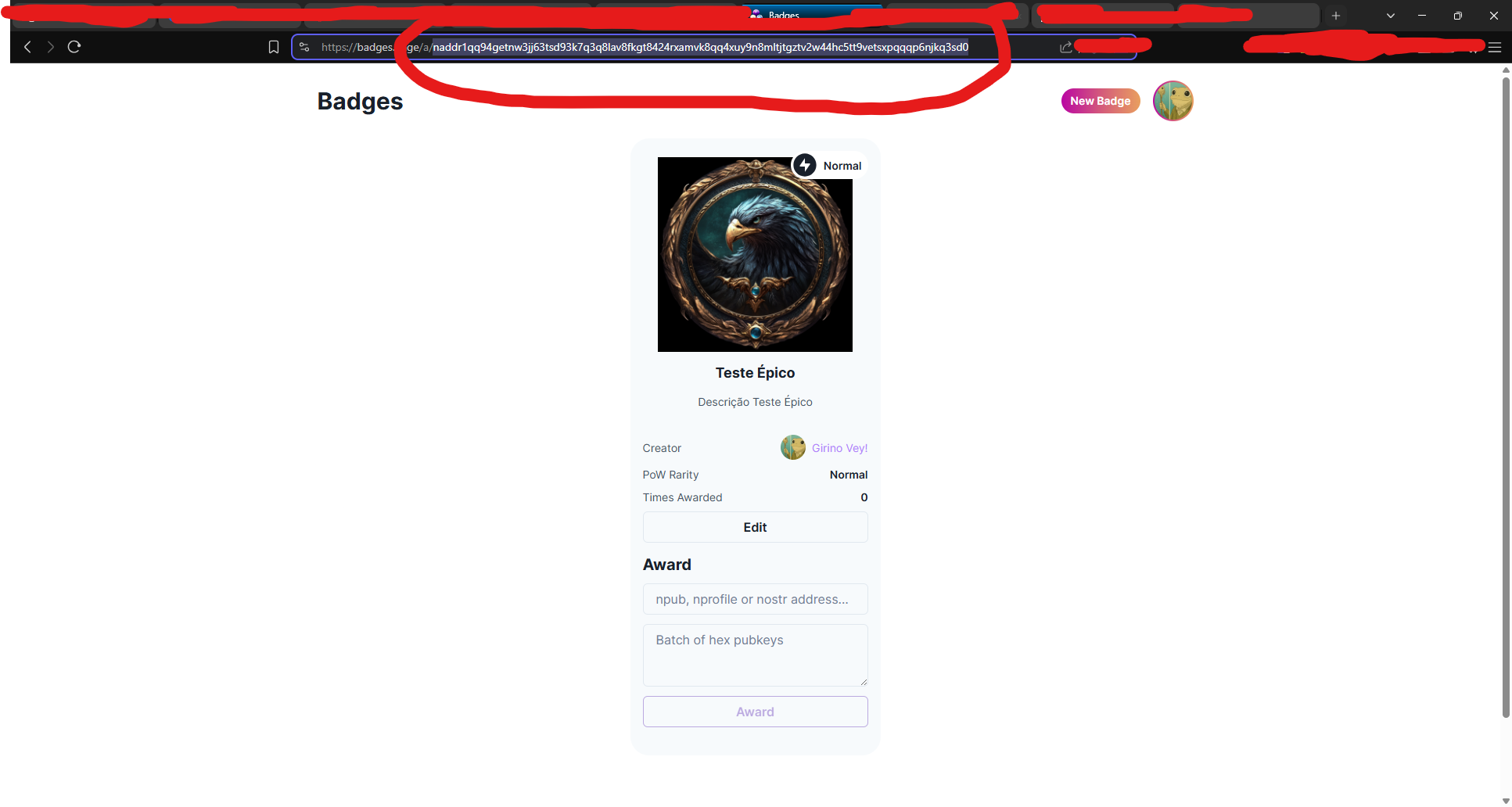
🧠 Passo 3 — Decodificar o naddr com
nakAbra seu terminal (ou Cygwin no Windows) e rode:
bash nak decode naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Você verá algo assim:
json { "pubkey": "3ffac3a6c859eaaa8cdddb2c7002a6e10b33efeb92d025b14ead6f8a2d656657", "kind": 30009, "identifier": "Teste-Epico" }Grave o campo
"identifier"— nesse caso: Teste-Epico
🛰️ Passo 4 — Consultar o evento no relay
Agora vamos pegar o evento do badge no relay:
bash nak req -d "Teste-Epico" wss://relay.primal.netVocê verá o conteúdo completo do evento do badge, algo assim:
json { "kind": 30009, "tags": [["d", "Teste-Epico"], ["name", "Teste Épico"], ...] }
💥 Passo 5 — Minerar o evento como "épico" (PoW 31)
Agora vem a mágica: minerar com proof-of-work (PoW 31) para que o badge seja classificado como épico!
bash nak req -d "Teste-Epico" wss://relay.primal.net | nak event --pow 31 --sec nsec1SEU_NSEC_AQUI wss://relay.primal.net wss://nos.lol wss://relay.damus.ioEsse comando: - Resgata o evento original - Gera um novo com PoW de dificuldade 31 - Assina com sua chave privada
nsec- E publica nos relays wss://relay.primal.net, wss://nos.lol e wss://relay.damus.io⚠️ Substitua
nsec1SEU_NSEC_AQUIpela sua chave privada Nostr.
✅ Resultado
Se tudo der certo, o badge será atualizado com um evento de PoW mais alto e aparecerá como "Epic" no site!
- Ter o
-
 @ 35da2266:15e70970
2025-04-16 01:04:34
@ 35da2266:15e70970
2025-04-16 01:04:34YlKEinOudCnMdPLWsavMMDzVnKL/aWAKv/PZJQ9HtzMYlIqryjULMf8dOid834XpRo2pBuoetZz1kU60TGbNIVWOKRy9XBEZAiEZ0E9Kts4uwLu0qMfz+4zJ1Yt9X0CS3NkqswmYGNwGh9bzR35r2AjsXIadUT0y5z1LRy24A8tTgKD3iCZnrk99JFerTbrr2QOSpnvo3QWCSSShNaX0tU4tbKsol+EwsbeRTa5msbTKxNPSBuwEJEsj0nupMTmy5lQm6AxNlczHqqQJ8mR2nyshC/pIEccq1MJgxqLTMPXz3iFETI6H5cZBtuvjgQWoM0yb3BkZQYHA9FAe7Flul/N9lNBP4W399VCPoTOqIClL5v/GS//xuRB+zaKH4L5GTShnwWE73t99LZwpyVtAE2yODPt96Pti7D+OZSnLDNA=?iv=KnkTcfYKLLwkmQVtFf2dcQ==
-
 @ c1e9ab3a:9cb56b43
2025-04-15 13:59:17
@ c1e9ab3a:9cb56b43
2025-04-15 13:59:17Prepared for Off-World Visitors by the Risan Institute of Cultural Heritage
Welcome to Risa, the jewel of the Alpha Quadrant, celebrated across the Federation for its tranquility, pleasure, and natural splendor. But what many travelers do not know is that Risa’s current harmony was not inherited—it was forged. Beneath the songs of surf and the serenity of our resorts lies a history rich in conflict, transformation, and enduring wisdom.
We offer this briefing not merely as a tale of our past, but as an invitation to understand the spirit of our people and the roots of our peace.
I. A World at the Crossroads
Before its admittance into the United Federation of Planets, Risa was an independent and vulnerable world situated near volatile borders of early galactic powers. Its lush climate, mineral wealth, and open society made it a frequent target for raiders and an object of interest for imperial expansion.
The Risan peoples were once fragmented, prone to philosophical and political disunity. In our early records, this period is known as the Winds of Splintering. We suffered invasions, betrayals, and the slow erosion of trust in our own traditions.
II. The Coming of the Vulcans
It was during this period of instability that a small delegation of Vulcan philosophers, adherents to the teachings of Surak, arrived on Risa. They did not come as conquerors, nor even as ambassadors, but as seekers of peace.
These emissaries of logic saw in Risa the potential for a society not driven by suppression of emotion, as Vulcan had chosen, but by the balance of joy and discipline. While many Vulcans viewed Risa’s culture as frivolous, these followers of Surak saw the seed of a different path: one in which beauty itself could be a pillar of peace.
The Risan tradition of meditative dance, artistic expression, and communal love resonated with Vulcan teachings of unity and inner control. From this unlikely exchange was born the Ricin Doctrine—the belief that peace is sustained not only through logic or strength, but through deliberate joy, shared vulnerability, and readiness without aggression.
III. Betazed and the Trial of Truth
During the same era, early contact with the people of Betazed brought both inspiration and tension. A Betazoid expedition, under the guise of diplomacy, was discovered to be engaging in deep telepathic influence and information extraction. The Risan people, who valued consent above all else, responded not with anger, but with clarity.
A council of Ricin philosophers invited the Betazoid delegation into a shared mind ceremony—a practice in which both cultures exposed their thoughts in mutual vulnerability. The result was not scandal, but transformation. From that moment forward, a bond was formed, and Risa’s model of ethical emotional expression and consensual empathy became influential in shaping Betazed’s own peace philosophies.
IV. Confronting Marauders and Empires
Despite these philosophical strides, Risa’s path was anything but tranquil.
-
Orion Syndicate raiders viewed Risa as ripe for exploitation, and for decades, cities were sacked, citizens enslaved, and resources plundered. In response, Risa formed the Sanctum Guard, not a military in the traditional sense, but a force of trained defenders schooled in both physical technique and psychological dissuasion. The Ricin martial arts, combining beauty with lethality, were born from this necessity.
-
Andorian expansionism also tested Risa’s sovereignty. Though smaller in scale, skirmishes over territorial claims forced Risa to adopt planetary defense grids and formalize diplomatic protocols that balanced assertiveness with grace. It was through these conflicts that Risa developed the art of the ceremonial yield—a symbolic concession used to diffuse hostility while retaining honor.
-
Romulan subterfuge nearly undid Risa from within. A corrupt Romulan envoy installed puppet leaders in one of our equatorial provinces. These agents sought to erode Risa’s social cohesion through fear and misinformation. But Ricin scholars countered the strategy not with rebellion, but with illumination: they released a network of truths, publicly broadcasting internal thoughts and civic debates to eliminate secrecy. The Romulan operation collapsed under the weight of exposure.
-
Even militant Vulcan splinter factions, during the early Vulcan-Andorian conflicts, attempted to turn Risa into a staging ground, pressuring local governments to support Vulcan supremacy. The betrayal struck deep—but Risa resisted through diplomacy, invoking Surak’s true teachings and exposing the heresy of their logic-corrupted mission.
V. Enlightenment Through Preparedness
These trials did not harden us into warriors. They refined us into guardians of peace. Our enlightenment came not from retreat, but from engagement—tempered by readiness.
- We train our youth in the arts of balance: physical defense, emotional expression, and ethical reasoning.
- We teach our history without shame, so that future generations will not repeat our errors.
- We host our guests with joy, not because we are naïve, but because we know that to celebrate life fully is the greatest act of resistance against fear.
Risa did not become peaceful by denying the reality of conflict. We became peaceful by mastering our response to it.
And in so doing, we offered not just pleasure to the stars—but wisdom.
We welcome you not only to our beaches, but to our story.
May your time here bring you not only rest—but understanding.
– Risan Institute of Cultural Heritage, in collaboration with the Council of Enlightenment and the Ricin Circle of Peacekeepers
-
-
 @ 35da2266:15e70970
2025-04-16 00:31:22
@ 35da2266:15e70970
2025-04-16 00:31:22LTcj+3KWI8XMzz4Ym2m+BueOuNcKP0mbeS59YLfrySjrf+xfAI8Xz/7qpW11EhahB67O2nZW2kMFfiaFpvDy53ot4a5MJ4Ab/Lt5d7Rg018eXygoPotWELDh69tGyb4nHZGL1APOFLBz0n+zYMceBoTT3cIyvZjtWLbsovCMaafxUWyx23cZ6DmgKizKKJDTQPFR+iVC1N3i/QOBVQb4Sl/iq2TR8J9gVbkOtU9wbZWp27zOamCI06FI0L+fLRLwVK39raNKLg4sHioRK5mbbRm1959NmezqF+LugdVfWoCfvn5IZjBj8j3cVJKeUfgKwg0dgq4M1/yPOTDM8d0NBIk3YXZAIQ0CcGYMfNCyVuY=?iv=da7j+e07uz89rJPwTNPAng==
-
 @ e968e50b:db2a803a
2025-04-15 13:47:13
@ e968e50b:db2a803a
2025-04-15 13:47:13There's really not much to say. I just wanted to put a bug in the ear of anybody else that has to deal with water problems and has a few old, unprofitable s9s sitting around. At least you'll get your KYC-free bitcoin rebate. Is there a business opportunity here?!?
originally posted at https://stacker.news/items/944025
-
 @ ba36d0f7:cd802cba
2025-04-06 16:34:37
@ ba36d0f7:cd802cba
2025-04-06 16:34:37| Pieza | Movimiento | Reglas Especiales | | --------- | ---------------------------------- | --------------------------- | | Peón | 1 casilla adelante (o 2 al inicio) | Captura al paso, coronación | | Torre | Líneas rectas | Enroque | | Caballo | En "L" (2+1) | Salta piezas | | Alfil | Diagonales | Atrapado en un color | | Dama | Cualquier dirección | Ninguna | | Rey | 1 casilla en cualquier dirección | Enroque, jaque mate |
1. Peón (♙ / ♟️)
-
Mueve: 1 casilla adelante (o 2 en su primer movimiento).
-
Captura: En diagonal (1 casilla).
> Especial: >- Captura al paso: Si un peón rival avanza 2 casillas, puedes capturarlo como si hubiera movido 1. > - Coronación: Al llegar a la 8ª fila, se convierte en cualquier pieza (¡usualmente Dama!).
2. Torre (♖ / ♜)
-
Mueve: Líneas rectas (sin límite de casillas).
-
Especial: Participa en el enroque.
3. Caballo (♘ / ♞)
-
Mueve: En "L" (2 casillas en una dirección + 1 perpendicular).
-
Única pieza que salta sobre otras.
4. Alfil (♗ / ♝)
-
Mueve: Diagonales (sin límite).
-
Siempre permanece en el mismo color de casilla.
5. Dama (♕ / ♛)
-
Mueve: Cualquier dirección (recto o diagonal).
-
¡La pieza más poderosa!
6. Rey (♔ / ♚)
- Mueve: 1 casilla en cualquier dirección.
Especial:
- Enroque: Cambia de lugar con una torre (si no hay obstáculos/jaques). - Jaque mate: Pierde si queda atrapado sin escapatoria.
Cómo mover
-
Un movimiento por turno.
-
Elige tu pieza y colócala en una casilla legal.
-
Solo tu color: Blancas mueven primero, luego negras, alternando.
-
No pasar: Debes mover si es tu turno.
Cómo capturar ("comer")
-
Ocupa la casilla de una pieza rival: Reemplázala con tu pieza.
-
Peones capturan solo en diagonal (no de frente).
-
Los reyes no pueden ser capturados (el jaque mate termina el juego).
✔ Jaque: Ataca al rey enemigo (debe escapar en su siguiente turno).
❌ Ilegal: Mover a jaque o dejar a tu rey en jaque.
Movimientos especiales
|Movimiento|Regla Clave|Notación| |---|---|---| |Enroque|Rey + torre, sin movimientos previos|
0-0| |Coronación|Peón→cualquier pieza en 8ª fila|e8=D| |Captura al paso|Captura un peón que avanzó 2 casillas|exd6 a.p.|
1. Enroque ("La escapatoria del rey")
-
Qué: Rey y torre se mueven juntos en un turno.
Cómo: -
Rey mueve 2 casillas hacia una torre.
-
Torre "salta" al lado opuesto del rey.
Reglas: - Sin jaques: El rey no puede estar en jaque ni pasar por casillas atacadas. - Sin movimientos previos: Ni el rey ni esa torre deben haberse movido antes.
Tipos:
- Corto (lado del rey, rápido):0-0- Largo (lado de la dama, seguro):0-0-0
2. Coronación ("Coronar")
-
Qué: Peón llega a la 8ª fila → se convierte en cualquier pieza (usualmente Dama).
-
Cómo: Reemplaza el peón (incluso si ya tienes esa pieza).
Dato curioso: Puedes tener 9 damas (1 original + 8 coronaciones).
Ejemplo: Peón en h8 se convierte en Dama →h8=D.
3. Captura al paso (Del francés "en passant")
-
Cuándo: Un peón rival avanza 2 casillas y queda al lado del tuyo.
-
Cómo: Captúralo en diagonal (como si hubiera movido 1 casilla).
Regla: Debes hacerlo inmediatamente (solo en el turno siguiente)
-
-
 @ 35da2266:15e70970
2025-04-16 00:29:18
@ 35da2266:15e70970
2025-04-16 00:29:18enNjYOtdn9VukMmUvKkHjOljcVk2g5KKH5PjjljxUuOABxqIGInmW1jqgF9+E5Unxcoi8mWNJtOrC6Br/z23XrZjc+tt2zxbe9gLbtfZnTxXRUD5BmLzQoENXlBfjZjV90Yzt0S04CdmNKTZVeeJETXKoXWWuwlx5GlRgMJiC92kZyk26muxi+Xvh9lxSxascUQELNlqY0ySXG4/Hg/K8qiFxVBB1ZU2kuK4EW5RU/5Su2gb5jpzjCsuYXfM5Nd05eehnbbdY8S0jt37/B2TzYfrim+iLJM4Nq1TX3pOoAGhZgSKoDbbCwu8xxsDdTDRc9sInaUn2obMb4w0ylH+ZYHwiuSiOW0anfLyUM2/NoYPX+ZEx57waSU7+2zbY66x?iv=uuQ35Xb0RNpJAn+GJVixKQ==
-
 @ 35da2266:15e70970
2025-04-16 00:15:02
@ 35da2266:15e70970
2025-04-16 00:15:02yf+dVZcg5m0ZWh0Vagoapkqo0p7GUDpcuicMVY3R1tN0pWbgiIT5auPs6+nIgD6fuCj8NpZYCI/ldesFKuBjowJxgq9WAKEgrVIkok9Mmes/7kjGP7aPzXyNBCmnrM3E8ZhmUI9YWCYZDNnrULkGPmco7HaTnMJOFqLUp6NzWtROYqV11HNVGG+H33blj0HA/HESPNaPbFDvw/2hGGf+XGzOaWfkRQFKvWIZJKPgMDAAJgMyUBHHEI6fkB8SICNWIT78Oj81JquMw448hMQ92a1aJu2tXNZiIyZ4AfioA/E0ZFK4DKaQ4V3Lav1DKr9iYIS1dOxZ/qAH3jsaTASgoLsgVISHEjFgFXO7VnTa8GfhzUHzgl/7fH/3OVnnYrwE?iv=UO8NRkvzZ3ApNXIkv5WSgw==
-
 @ ba36d0f7:cd802cba
2025-04-06 16:21:23
@ ba36d0f7:cd802cba
2025-04-06 16:21:23Configuración del Tablero
-
Lo Básico
Tablero de 8x8 casillas, alternando colores claros/oscuros.Regla: Siempre coloca el tablero con una casilla clara en la esquina inferior derecha de cada jugador.
-
Coordenadas
-
Columnas (files): Letras a a h (de izquierda a derecha).
-
Filas (ranks): Números 1 a 8 (fila 1 = lado blanco, fila 8 = lado negro).
>Notación: Cada casilla es columna + fila (ej. e4, a7).
-
-
Colocación de Piezas
Negras (Parte superior):- a8: Torre | b8: Caballo | c8: Alfil | d8: Dama
e8: Rey | f8: Alfil | g8: Caballo | h8: Torre
Fila 7: Todos los peones (a7-h7).
Blancas (Parte inferior):
- a1: Torre | b1: Caballo | c1: Alfil | d1: Dama
e1: Rey | f1: Alfil | g1: Caballo | h1: Torre
Fila 2: Todos los peones (a2-h2).
Consejo: Las damas empiezan en su color (blanca en d1, negra en d8).
- a8: Torre | b8: Caballo | c8: Alfil | d8: Dama
Jaque mate, ahogado y tablas
El ajedrez es un juego de estrategia donde el objetivo es dar jaque mate al rey rival. Pero también puede terminar en ahogado o tablas bajo ciertas condiciones.
-
Jaque Mate (Victoria)
-
Definición: El rey rival está en jaque (bajo ataque) y no tiene movimientos legales para escapar.
-
Resultado: Fin del juego — el jugador que da jaque mate gana.
-
-
Ahogado (Tablas)
-
Definición: El jugador en turno no tiene movimientos legales, pero su rey no está en jaque.
-
Resultado: Tablas (empate).
-
Causas comunes:
-
Un rey solo sin movimientos.
-
Estructura de peones que bloquea todas las opciones.
-
Otras Situaciones de Tablas
-
Material Insuficiente:
-
Solo quedan los reyes.
-
Rey + alfil vs. rey (no se puede dar jaque mate).
-
-
Triple Repetición:
- La misma posición se repite 3 veces (con el mismo jugador en turno).
-
Regla de los 50 Movimientos:
- Sin capturas ni movimientos de peón en 50 jugadas consecutivas.
-
Acuerdo Mutuo:
- Ambos jugadores aceptan tablas.
-
Diferencias clave:
|Término|¿Rey en Jaque?|¿Movimientos Legales?|Resultado| |---|---|---|---| |Jaque mate|Sí|No|Victoria/Derrota| |Ahogado|No|No|Tablas| |Tablas|N/A|N/A|Empate|
Historia del Ajedrez
-
Orígenes (Siglo VI)
-
Nacimiento: Norte de India (como Chaturanga), con cuatro divisiones militares (predecesoras de peones, caballos, alfiles y torres).
-
Expansión: Llegó a Persia como Shatranj (año 600 d.C.), donde surgieron términos como "jaque" y "jaque mate".
> Dato curioso: "Jaque mate" viene del persa "Shah Mat" ("el rey está atrapado").
-
-
Europa Medieval (Siglos IX–XV)
-
Adaptación: Los árabes llevaron el ajedrez a España (1000 d.C.); los europeos cambiaron las piezas:
Elefantes → Alfiles
Visires → Damas (¡al inicio solo movían 1 casilla!) -
Cambio clave: Hacia 1475, la dama se convirtió en la pieza más poderosa ("Ajedrez de la Dama Loca"), acelerando el juego.
-
-
Ajedrez Moderno (1850–Actualidad)
-
Estándares: Primer campeonato mundial oficial (1886, Steinitz vs. Zukertort).
-
Computadoras: Deep Blue de IBM venció a Gari Kaspárov en 1997, revolucionando la IA.
-
Hoy: Plataformas online (Chess.com, Lichess) y series (Gambito de Dama) popularizan el juego.
-
¿Sabías Qué?
-
La partida teórica más larga posible es de 5,949 movimientos.
-
La partida real más larga duró 269 movimientos (Nikolić vs. Arsović, 1989).
-
La apertura más antigua registrada (1.e4) aparece en un manuscrito español de 1490.
-
-
 @ d3d74124:a4eb7b1d
2025-04-15 12:58:08
@ d3d74124:a4eb7b1d
2025-04-15 12:58:08ORIGINALLY ON XITTER BY STEVE BARBOUR. SHARED HERE FOR THE HOMIES (https://x.com/SGBarbour/status/1911614638623801425)
I find bureaucracy fascinating—it’s like a cancer within human organizations.
Why do organizations become bloated with excessive procedural controls, inefficiency, and indecisiveness as they grow in size and age? Why does decision-by-committee often replace the ambitious, self-starting decision maker? Why do small, "lean and mean" startups inevitably become bloated with bureaucracy as they scale and increase their headcount?
In 2014, these questions consumed me while I sat in a cubicle at an oil and gas company. Why, after years of honing my skills to fix artificial lift systems, was my signing authority decreasing (from $25,000 to $10,000 for workover budgets), despite record corporate profits? Why did I now need a 12-page Microsoft Word document with manager sign-off to schedule and scope a service rig for a simple pump change, when a five-minute email direct to the rig supervisor had previously sufficed?
Years into the job I was far more capable than when I had started, yet I had less authority with each passing day. I became determined to understand what was causes bureaucracy and whether or not it can be prevented.
After researching for some time, such as the essay I posted below, I concluded that bureaucracy stems from a lack of trust and accountability. Bureaucrats impose procedures instead of trusting subordinates to do their jobs, often in response to a costly mistake. This results in new processes that everyone must follow.
Bureaucrats rarely take responsibility for their own failures or hold others accountable for theirs. Instead, they create more procedures and invent new processes. Bureaucracy is a systemic issue, pervasive in nearly every large business or institution. The larger the organization, the more stifling it becomes.
This behavior is costly, increasing administrative overhead and delaying capital execution. Who is bearing this enormous cost?
You are, of course!
Fiat money funds the vast majority of the world's bureaucracy. Fiat money is counterfeit created out of thin air and is used to fund deficit spending by governments worldwide. Governments use paper money they did not earn from taxes to bail out institutions who are overleveraged and get caught with their pants down (e.g. Bombardier and Air Canada are famous repeat offenders in Canada, in the US you can choose any big name bank just about).
They keep printing money and nobody is held accountable anywhere.
Misallocate capital, become insolvent, print money and bail out, create new regulations / procedures, repeat.
You pay for bureaucracy by losing your savings to inflation.
You pay for bureaucracy when the local small businesses in your neighborhood is replaced by a global franchise funded by cheap, perpetual fiat money.
You pay for bureaucracy when you cannot retire as early as you planned and end up working yourself straight into a retirement home.
I was cleaning and organizing my office today and found this old essay by Brian D. Rule from 1977 on the topic, which sparked me to write this short X piece on bureaucracy.
Brian's essay 'Bureaucracy' was actually the very essay that led me into believing fiat money with the root cause of global bureaucracy and waste, which lead me to become interested in gold in 2015 and then in bitcoin in 2016.
Sure enough I googled the prevalence of the term 'bureaucracy' and something interesting happened after 1971...
Isn't it weird how so much went to shit after we got off the gold standard?
Today I am convinced that hard, sound money is the only solution to bureaucracy. This is why I work for #bitcoin.
*Sadly I can no longer find the essay online, so I ripped the text from my paper printout that I found in my files with the now defunct reference website below. *
Bureaucracy
Brian D. Rude, 1977
Original website (now defunct): http://brianrude.com/burea.htm
In the summer of 1975 I took a teaching job in Nebraska. As my previous teaching experience was in Missouri I had to see about getting a Nebraska teaching certificate. I applied for a "Nebraska Standard" teaching certificate. I sent in my college transcript, the application form, and a check for eight dollars. They sent me back, in their own good time, a "Nebraska Prestandard" certificate. I decided there was nothing "prestandard" about me or my teaching, so I wrote back and asked why I didn't get the "standard" certificate. They replied that since I had not taught three out of the last five years I was eligible only for the "prestandard" certificate.
"What do those pigheaded bureaucrats know about my teaching?" I thought to myself. "How would they ever know the standard of my teaching just from shuffling papers around?"
With a little reflection I realized that of course they know nothing about my teaching. They are not supposed to know anything about my teaching. They are paid to evaluate the papers I send them. They are not paid to evaluate my teaching. They have a clear mandate to shuffle my papers, and nothing more.
I presume my application was opened by a secretary, who, following a tightly structured routine, checked off each requirement, typed up my certificate, got it signed by some authority and sent it off to me. Such a secretary is most likely a conscientious worker, a wife and mother, a Republican or Democrat, an occasional churchgoer, a bit of a gossip, and a lot of other plain ordinary things. But she is most likely not a "pigheaded bureaucrat". She would not think of herself as a bureaucrat, and neither would her boss, her coworkers, her family, or anyone else who personally knew her. When she typed "prestandard" instead of "standard" on my teaching certificate she is simply doing her job. Were she to do anything less or more she would be negligent.
So where is the bureaucracy? Or was I dealing with a bureaucracy? If not, then where is there a bureaucracy? Where do we find the genuine article, the bungling, myopic, pigheaded bureaucrat?
I think pigheaded bureaucrats do exist, but they are rare. It's the good bureaucrat that drives us batty, quite as much as the bungling bureaucrat. The good bureaucrat knows exactly what he is obligated to do and he does it conscientiously. The good bureaucrat simply applies the rules that he is responsible for applying, but that he did not make.
A bureaucracy is a group of people responsible for applying a set of rules. The police, courts, executive branches of government, parents, teachers, librarians, and many other people or groups of people are also responsible for applying rules, yet we don't think of these as being bureaucracies. The distinguishing features of a bureaucracy are the types of rules to be applied, and, to some extent, how the rules are applied.
A bureaucracy is responsible for applying what I will call "secondary", or "derived" rules. A secondary rule is a requirement or prohibition established only because it promotes a primary goal. When Moses came down from the mountain with his stone tablets he was carrying what might be considered the simplest statement of what I will call "primary" requirements. The rule, "Thou shalt not steal", for example, is a primary requirement because it is desirable for its own sake, not just as a means to some other end. Similarly, "Thou shalt not commit murder" is a primary requirement because it is desirable as an end in itself.
Safe driving, as a modern example, is a primary requirement because it is desirable for its own sake. The requirement that one get a driver's license before driving, in contrast, is a secondary requirement. It is a requirement instituted by state governments in an attempt to promote the primary goal of safe driving. It is secondary to, or derived from, the primary requirement of driving safely. If people always drove safely, or if driving by its nature presented no hazards, then there would be no need for driver's licenses. Or if legislatures decided that licensing did nothing to promote safe driving then there would be no need for driver's licenses. Licensing is not an end in itself.
Tertiary, or third order, requirements can also exist. If a state requires a birth certificate as proof of age before issuing a driver's license then the state is imposing a third order requirement. Showing a birth certificate is a requirement designed to promote the licensing of drivers, which in turn is designed to promote safe driving.
I imagine one could go ahead and find examples of fourth order requirements established to promote third order requirements. However I don't think there is much point in getting too deep in this kind of analysis. The main point is the distinction of whether a goal is important for its own sake or whether it is important in promoting some other goal. Thus I may speak of a "derived" requirement, meaning only that it is not a primary requirement, but not specifying whether it is secondary, tertiary, or even further removed from the primary goal.
In different contexts I may speak of primary or secondary "requirements", "rules", "prohibitions", "laws", "regulations", "goals", "wrongs", "burdens", "privileges", and so on. It seems natural to think of paying taxes as a "requirement", while murder is a "wrong" that is covered by a "prohibition". But the requirement of paying a tax can be interpreted as the prohibition of avoiding the tax, and the prohibition against murder can be interpreted as the requirement to refrain from murder. The important point here is the distinction between primary and derived, not between omission and commission.
In the example I gave about getting a teaching certificate the bureaucrats were concerned only with my compliance with secondary requirements. They were not at all concerned with the primary requirement - the requirement that I indeed be a good teacher. This is a distinguishing characteristic of bureaucracies. They are concerned only with applying derived, not primary, rules. Other agencies are brought in when there is a primary rule to be applied. The police and courts handle such primary wrongs as theft and murder. Parents and teachers handle such primary wrongs as tracking mud on the carpet or being late to school. Churches handle such primary wrongs as "living in sin" or blasphemy. But it doesn't take a judge or a preacher to decide if my application for a teaching certificate is in order, or my application for a driver's license, or a dog license, or a business license, or a barber's license, or a building permit, or a marriage license, or breathing license. It takes a bureaucrat to handle these matters.
The basic root of bureaucracy then, is the proliferation of secondary requirements. It is not enough, in our modern world, to just be a good and honest person. One can be the best and safest of drivers, but a driver's license is still required. One can be a patriot and a saint, but the IRS still wants that W-2 form. One can be the best doctor in the world, but to practice medicine without a degree and a license is still a serious offense. We have established literally millions of secondary requirements designed to promote a few primary goals. To administer these rules we have people we call bureaucrats.
If the basic root of bureaucracy is a proliferation of derived requirements, then it would seem reasonable that the way to decrease bureaucracy would be to decrease such requirements. This is true, and in fact is a main thesis of this article. Unfortunately it is not always easy to do. Every bureaucratic requirement, in a healthy society at least, was established by reasonably intelligent people giving at least half-way serious consideration to a genuine problem. Therefore any particular bureaucratic requirement or procedure that is challenged will be defended by some person or group.
The most important gain we hope to realize from derived requirements is security. The requirement of any permit or license is usually, if not invariably, justified in order to "protect the public". We want safe driving so we demand driver's licenses. We want our neighbor's dog out of our flower bed so we demand dog licenses. We want merchants to be honest so we demand business licenses. We want welfare recipients not to cheat so we require verification of identity, employment, and who knows what else. All these requirements are seen as necessary to prevent something bad from happening, or to assure that something good will happen.
Derived requirements cannot provide all types of security. We can't prevent floods and famines by making rules and printing forms. The type of security that is the goal of bureaucratic requirements is social control of one form or another.
Simple fairness is often the goal of bureaucratic requirements. The Internal Revenue Service is a good example of this. The primary goal of the IRS is to raise money. This could be done by charging every citizen a flat rate of $1000 or so each year. We wouldn't consider this fair, though, because we realize not everyone has an equal ability to pay. Therefore we have an elaborate set of rules designed to extract more from those who have more. To apply these rules we have what is probably the biggest and most complex bureaucracy since time began. This size and complexity comes from our desire to be fair, not from the simple desire to collect money.
Another form of social control for which bureaucratic requirements are established is prevention of abuse of power. Power comes in many different forms, and we know from long experience that power is always susceptible to abuse. One method of dealing with abuse of power is to call it a primary wrong and punish the offenders. This is done, and it keeps the police and courts very busy. Another way to control abuse of power is to set up secondary requirements to try to prevent such wrongs from occurring in the first place. This produces bureaucracies. In the 1880's, for example, railroads were playing a little rougher than people wanted. They gained power by monopolizing a vital service. In response to this the Interstate Commerce Commission was set up, and has regulated business ever since. A more modern, and more specific, example would be the requirement that a used car dealer certify that the odometer reading is correct when he sells a car. This requirement is in response to what is seen as abuse of power by car dealers who misrepresent their merchandise.
In addition to the main cause of bureaucracy - the proliferation of derived requirements for purposes of security - there are several other causes of bureaucracies that are worth mentioning. The first of these is pure blind imitation. Again I will use driver's licensing as an example.
In the fifty states there is a startling uniformity of driver's license requirements. The most obvious uniformity is that all states require licenses. I have never been able to understand this. It would seem that if each state followed its own experience, values, customs, and judgment, then there would be a whole spectrum of licensing requirements, ranging from no requirement at all to extensive and strict requirements. This is apparently not the case. The majority of states require a written, driving, and eye test. They require a license fee. They require renewal of the license every so many years. They require that the license be in the person’s possession while he is driving. So far as I can tell only minor variations are found on this basic pattern in the different states.
I attribute this uniformity mainly to imitation. If there were an obvious connection between traffic safety and driver’s licensing then this uniformity would seem more sensible. If the National Safety Council told us everyday that the majority of fatal accidents involved an unlicensed driver, then we would not be surprised to find a driver’s license requirement in every state. But that is not the case. The National Safety Council talks a lot about the drinking driver but not about the unlicensed driver. If there was a historical example of some state that was too stubborn to require licenses and had an atrocious accident rate, then again a strict licensing system would be expected in every state. But is not the case either. The connection between licensing and safe driving is tenuous at best. There are innumerable unsafe drivers in every state who have no trouble getting a license. There are also perfectly safe drivers who have trouble getting a license. I think it is safe to say that the average driver, safe or unsafe, can’t pass the written test without studying the book no matter how long he has been driving. Many people find this out when they try to renew their license. All this leads me to believe that licensing requirements are set up by imitation more than anything else. A few states started requiring licenses and other states blindly followed, thinking in some vague way that they were being modern and progressive.
Pure blind imitation may seem a poor reason to set up a bureaucratic requirement and a bureaucracy to apply it, but there are many examples of such imitation in everyday life. In a previous article, ("Roting and Roters", not yet on my web site) I described and developed the idea that blind imitation is a powerful determinant of individual behavior. I think it is almost as powerful a determinant of group action. If each state followed its own inclination in the matter of driver’s licensing I would expect a much wider variation among the different states.
Another cause of bureaucracies is a little more substantial than blind imitation, and accounts for many licensing systems. That is the desire for group recognition. People are by nature social animals. They want to have groups and they want to do things in groups. They want their groups to be recognized and they want this recognition to be official and formal. I began to realize this a few years back when I read in the paper that beauticians were trying to get legislation passed setting up a system of beautician licensure. I thought they were nuts. Why, when we all hate the bureaucracy so much, would anyone want to set up more bureaucracy?
Another example of this kind of bureaucracy building is in the field of occupational therapy. Nurses, physical therapists, and speech therapists are licensed by the state. Occupational therapists, in contrast, have a national association which gives a "registry examination". Upon passing this test, and having a degree in occupational therapy, one becomes an "O.T.R.", a registered occupational therapist. Hospitals and other institutions take this designation as evidence of full qualification in the field. With such a sensible system I find incomprehensible that the profession is pushing for a system of state, rather than national, licensure. But that is exactly what they are doing. They are trying to build more bureaucracy, and they will succeed.
It took me quite a number of years to realize that teacher certification is something that the teaching profession wants, rather than being a requirement imposed from above. However that is apparently the case. The system of licensure, though a pain, does give some recognition to the status of teachers. This, along with a considerable amount of blind imitation, apparently accounts for the uniformity of teacher certification requirements found in different states.
It would be nice if we could give official recognition to groups without the necessity of laying down a mass of secondary requirements, but that is not how it works. Recognition, apparently would have little meaning if it did not indicate that the members of the group meet a system of requirements. It would also be nice if those who gain this official recognition were always worthy of it, but that also is unfortunately not the case. There will always be drivers, teachers, beauticians, occupational therapists, doctors, lawyers, and others who somehow manage to gain the official license but are recognized by their peers as incompetent. Whenever a system of secondary requirements is established there inevitably enters a "reality gap", a gap between the ideal and the real. This can make the whole system ineffective. I will have more to say about this ineffectiveness and its effects shortly.
Yet another factor leading to the spread of bureaucracy is a systematic error made, to a greater or lesser extent, by practitioners of almost any field. That error is thinking that the world’s problems will be solved by one’s own field of knowledge or mode of operation. I think a good name for this would be "role egocentrism". Egocentrism means that a person considers himself the center of the universe, just as ethnocentrism means that a group considers itself the center of the universe. Role egocentrism simply means that one’s own role is given undue importance and status. Thus doctors think that medicine will be the salvation of the world. When medicine has progressed far enough, they think, the world will be such a fine place that other problems will just disappear. Preachers think that if only we would all turn to God there would be no more problems. Farmers think that once the world food problem is solved, by farmers of course, then all will be well. Teachers think that education will be the one thing to save mankind from itself. Scientists think that research will usher in a new golden age.
It is hard to conceive of a bureaucrat having such grandiose visions of salvation. But remember that bureaucrats do not think of themselves as bureaucrats. Even more importantly, bureaucrats don’t make the rules, they only apply them. The rules are made by governments. Governments consist of politicians, and politicians are very susceptible to role egocentrism. To attain office a politician must convince people that government is capable of doing things, and he must believe it himself. Since people want things done it is not surprising that governments are populated by large numbers of people with an inflated idea of what can be done by writing rules and laws. Since there are few primary laws left to write, we have an ever-increasing proliferation of secondary requirements. Bureaucrats may not make the basic rules that they apply, but they do have some latitude to make minor rules, and even more importantly, they are responsible for making reports and can require reports from their subordinates. In the making of reports a little role egocentrism can go a long way. The result can be a massive flow of reams and reams of paperwork, with copies sent to all other bureaucrats who might have come slight connection to the job at hand, but with very little of the reports actually being read.
Bureaucrats also have some latitude in working as individuals or teams, and again a great deal of waste can ensue. The justification for working in committees or teams is the idea that by joining forces the best abilities of each member can be brought to bear on the problem at hand and therefore a solution to the problem is more likely. Of course there is some truth to this, but it doesn’t always work out too well. The little bit truth can become greatly augmented by role egocentrism. Team workers like to think that if you set six experts around a table something good is bound to come out of it. Non-team workers, like myself, tend to think that setting six experts around a table is a good way for six experts to waste each other’s time. I think bureaucrats at the higher levels are more prone to waste their energy this way, and I interpret this as a form of role egocentrism.
All of these cases of bureaucracy are augmented by another systematic error. That error is the systematic overestimation of group cohesiveness. In the minds of bureaucracy builders the bureaucracies already in existence become "they", and "they" are a bunch of pigheaded fools. "We", on the other hand, are good, right-thinking people and the bureaucracy we set up will serve the people, not the bureaucrats. And just to make sure we’ll write in plenty of safeguards. Of course this doesn’t work. Just because it is "our" program doesn’t mean that it won’t be subject to all the problems that beset any program. A new generation will grow up and decide that "we" are "they" and the cycle begins over again.
So far I have painted a rather pessimistic picture. We have bureaucrats because we have a multitude of derived requirements to administer, and we have a multitude of derived requirements because we think they bring us security. We also have bureaucracies because of imitation, because of the desire for group recognition, and because of role egocentrism. Yet the sum total of all this drives us batty. The next step is to try to get some idea of why and how bureaucracy is frustrating. I think the frustration results from main causes, standardization and ineffectiveness.
Standardization is a wonderful thing in industry. If my car needs a new fuel pump I can buy one right off the shelf and know it will fit. Fuel pumps are standard, and engines are standard. They fit together beautifully. The few defective fuel pumps that are not standard are quickly caught and tossed off the assembly line. This happy state of affairs does not extend to non-physical objects though. Consider, for example, a seed planter. I don’t know just how a planter might work but I visualize a mechanical hand grabbing one seed at a time and popping it into the ground. Seeds are pretty well standardized and most seeds can be picked up by these mechanical hands without injury. A few seeds, however, are nonstandard. They are either too big, or too small, or perhaps the wrong shape. The iron hands that so effectively plant most seeds will bruise, shred, mangle or maybe just overlook the oddball seeds. This doesn’t worry us though. Just like the defective fuel pumps that are bumped off the assembly line, the few mishandled seeds are of no great consequence.
When standardization is extended to humans the situation changes dramatically. We can’t bump off the defectives so carelessly. A bureaucracy can be compared to the seed planter. Iron hands pick you up and set you down again. If you fit the standard mold, these iron hands hold you gently. If you don’t fit the standard mold those same iron hands can shred you to pieces.
For example, a few years back I knew a fellow who was paraplegic. He was completely confined to his wheelchair, but he had a car with adapted controls and could drive as well as anyone. Unfortunately he had considerable difficulty licensing both himself and his car. He could drive to the courthouse, and get himself out of his car and into his wheelchair, but he had no way of getting down in the basement where the licensing offices were. There were elevators from the first floor to the basement of course, but between the parking lot and the first floor were innumerable steps and curbs. To a person in a wheelchair a single four-inch curb might as well be a ten-foot wall. Apparently my friend managed somehow to keep himself legal most of the time, but he did at times speak bitterly about the troubles he encountered. The state required licenses, and the state provided a way to get these licenses, but only if you fit the standard mold. My friend did not fit the standard mold, and felt very much caught in those iron hands.
Fortunately most examples of the problems of standardization are not so serious. My wife had a friend in college who was triply enrolled in the School of Education, the School of Medicine, and the Graduate School. All occupational therapy students were dually enrolled in Education and Medicine, which caused no end of red tape in itself, but this particular girl was such a go-getter that she added Graduate School. This made her a non-standard person indeed. One day she spent a solid half hour on the phone trying to convince some bureaucrat that, no matter that it didn’t fit the computer, it was possible to be enrolled that way. I presume the problem, whatever it was, was eventually worked out, but not without some cost in frustration. The bureaucrat in question was probably no more pigheaded than you or I. The rules he was responsible for applying simply made no provision for triply enrolled students.
When caught as a non-standard person in a standardized bureaucracy one wonders why standardization is established in the first place. Except for the role egocentrism of a few bureaucrats, standardization is not intentional. It arises by the same forces that promote standardization in industry. Standardization promotes efficiency. Whenever a form is printed, for instance, it is designed to fit the majority of situations. Thus a fire insurance application form may ask if the house is frame or brick, with no intention of frustrating the owners of igloos, caves, and houseboats. It simply reflects the fact that most houses are either frame or brick. By stating these two choices the processing of the application is speeded up. If instead the application stated simply, "describe the dwelling to be insured", the work in processing the application would be considerably increased. Standardization is the inevitable correlate of the proliferation of secondary requirements.
There is also another cause of standardization, the lack of discretionary authority. Remember that secondary requirements are set up in many cases to prevent abuse of power and to be fair. This usually means that the bureaucrats who apply these rules have only a limited number of responses to a given situation. Bureaucracies are given very little discretionary authority. They must follow the rules whether the rules fit the situation at hand or not. To illustrate this let me hypothesize two ways of administering welfare.
In case A an applicant comes to a social worker. The applicant explains that her husband just lost his job because he drank too much, that she works as a maid two days a week but that her children have no one to stay with them when she works unless she pays a baby sitter which costs almost half her salary, that their car is about to be repossessed and then she won’t be able to get to work at all, that the landlord won’t fix the plumbing and charges too much rent, that they would move except they haven’t found a place that’s any cheaper, that their oldest son was just sent to jail for a two year term, and on, and on, and on. The social worker listens to all this, makes a few phone calls, and the next day tells the applicant, "We’ll give you $70 a week allowance, but tell your husband to come in before next week. We’ll get him off his beer and on the job one way or the other. I called your landlord and got his side of the story and there’ll have to be a few changes made before he’ll reconnect the shower, and you’ve got to..."
In situation B the applicant comes to the social worker with the same story. The social worker says, "I think we can help you, but first you’ll have to find your birth certificate. Regulations state that only citizens are eligible for welfare. Then you’ll have to take this form to your employer to certify your wage scale. And this form goes to your landlord to verify your rent. And you’ll have to fill out this form to show how you budget your income, and this form to verify that you are not now receiving veterans or disability compensation, and this form that verifies you are not eligible to collect child support from any previous husband, unless the marriage was annulled, in which case you have to hunt up the certificate of annulment... What? You lost your certificate of annulment? You’re not sure you ever were married to John before you left him for Henry? ..."
In situation A the social worker is given a budget and a wide latitude on how to distribute the money. She is given discretionary power to a large degree. In situation B the social worker is given a very small amount of discretionary power. She can’t decide for herself whether the applicant is genuinely needy, but must prepare a "work-up", consisting of documentation of all relevant aspects of the applicant’s situation. On the basis of this work-up she is allowed to authorize an allowance, the amount to be taken from a table. If the social worker feels that there are relevant circumstances that are not covered at all in the standard work-up then she may begin some special procedure to have the case considered by a higher authority or committee. But the common suspicion that things aren’t quite as they should be, either because the applicant is undeserving or that he needs more than he can get or that the program misses its mark in yet some other way, is just a routine part of the job.
Standardization, fitting everyone into the same size slot, reduces everything to paperwork. The "work-up" is a stack of documents. These documents, certificates, forms, statements, memos, become the currency of bureaucracy, the medium of exchange. "Facts" become so only when they are certified by someone’s signature, even though they may be obvious. Other "facts" must be accepted because of their official certification even though common sense or simple observation show them to be false. A gap between the real and the official inevitably sets in. Then this gap leads to actions that are perceived to be detrimental or unfair, then the result is a considerable amount of frustration, in spite of the fact that the intent of all the red tape was to be beneficial and fair.
This leads to the second cause of bureaucratic frustration, which is ineffectiveness. If a bureaucratic requirement is seen as effective in accomplishing its goal we accept it even if there is considerable inconvenience involved in meeting the requirement. If, on the other hand, a bureaucratic requirement is seen as ineffective then a little inconvenience in meeting the requirement can be a very significant frustration. Getting a loan from a bank, for example, involves considerable effort in meeting bureaucratic requirements. However we don’t expect money to be handed out without some security that it will be paid back. Therefore we don’t get too frustrated by the inconvenience in meeting those requirements. Similarly, driver’s licenses are seen as worthwhile, even if not fully effective, and entail only a little bother every four years or so. Therefore we do not hear too much about pigheaded bureaucrats at the driver’s license bureau. Unfortunately other licensing systems have imperfections so massive and ubiquitous, and benefits so doubtful, that the whole system is a burden to society. A little inconvenience in getting such a license can be very frustrating. This is the frustration I felt in the example I gave at the beginning of this article about getting a teaching certificate. Another example would be going back three times to the fire station to get a bicycle license. I went back twice. I figured three times was above and beyond the call of duty. I never did get my bicycle licensed.
In psychological phenomena the whole is not always equal to the sum of its parts. Bureaucratic frustration can work this way. One frustration may be brushed off, and then another, and perhaps several more, but eventually there comes a point where the frustrations increase out of proportion to their cumulative value. Short-term frustration changes into long-term demoralization. I think "hassle" is a good name for this. It is a commonly used term, though it is not normally considered a specifically defined term. I think the phenomenon should be taken seriously though. It will become increasingly common with constant increases in bureaucratic requirements.
The best example I can give of hassle in my own experience comes from my home state of Missouri. To get one’s car licensed in Missouri one must show the title or previous year’s registration certificate, as can be expected, but that is not all there is to it. One must also get a new safety inspection certificate and also show his personal property tax receipt. When I lived in Missouri I usually didn’t have any property to be taxed, but I still had to go to the Treasurer’s office in the courthouse to get a card stating that no taxes were due. The safety inspection always caused me worry, and the car licensing itself always had the potential for problems. Maybe they would find something wrong with my title and tell me I can’t register the car. Thus the sum of all this was to me a hassle. The requirements exceeded my tolerance. It caused me anxiety, much more than the sum of the anxieties of each requirement had they come independently. Fortunately other states I have lived in didn’t tie those things together, and for that reason I hope I don’t end up living in Missouri again.
People vary in their susceptibility to hassle. I expect I have about as low a tolerance as anyone. I haven’t heard other Missourians complaining about the car licensing system. Unfortunately those who are not susceptible to the demoralization of hassles have little understanding of the anxieties of those who are susceptible. This goes along with the general rule that the more aggressive cannot empathize with the less aggressive. This increases the problem to those who are susceptible to hassle. However I would expect the future will see the problem given much more recognition as more and more people find themselves pushed beyond their tolerance.
A movement is currently under way by the Democratic Party to do away with traditional voter registration practices and to substitute a "same day" standardized registration system. Thus a voter could show up on election day, show proof of identity and residence, and be registered on the spot. The rationale of this is that the complications of regular registration are sufficient to prevent many people from voting. I think the move is clearly motivated by the political goal of increasing the Democratic vote. Still, I am glad to see the movement. They are talking about hassle. They are acknowledging that bureaucratic requirements are a burden, and that this burden can at times be of a serious nature. Now when somebody tells me I’m nuts if I worry about getting a car license I can reply that apparently some people worry about voter registration.
In the first part of this article I tried to explain the causes of bureaucratic requirements. Then I tried to analyze how bureaucracy produces frustration. There are very good reasons for bureaucracies, and there are very good reasons for frustration, so it appears we must live with the problem forever. I don’t think the world will grind to a halt though. The way out of this dilemma is simply to realize when diminishing returns begin to set in, and even more importantly, to realize when the return does not equal the investment. Every human endeavor has a cost and a benefit, an investment and a return. When establishing a system of secondary rules the investment includes the cost of setting up the bureaucracy, the cost of the individual’s efforts in dealing with the bureaucracy, and increasingly more importantly, the cost in frustration, anxiety, and demoralization. These costs must be subtracted from the benefits before deciding that a given proposal is or is not worthwhile.
Sometimes the cost can be reduced to dollars and cents. According to an item in the newsletter from my representative in Congress the town of Faith, South Dakota, recently applied for a federal grant. I believe they wanted to build a rodeo grandstand. They were offered $150,000 to match their own $50,000, but of course there were strings attached. After looking closely at these strings they finally rejected the federal help entirely and built their own grandstand for only $20,000. I doubt that this example is typical of federal grants, but it does illustrate diminishing returns.
More commonly only part of the cost can be reduced to dollars and cents. For example, an accountant may compute that a $20,000 grant for a town would entail only about $6000 in labor to do all the paperwork. This would seem to make a clear profit for the town of $14,000. But if the city officials are sick of the paperwork and the delays, if the citizens are mad at everyone and each other, and if the strings will be attached forever, then all this must certainly be subtracted from the benefit.
The investment/return assessment is even more complicated when all important factors are psychological. How can we put a price on invasion of privacy? How can we put a price on independence and respect for the individual? How are these costs to be subtracted from the safety and security that we gain from bureaucratic requirements? I don’t know. Since psychological costs cannot be measured in dollars and cents, the worth of any system of bureaucratic requirements will always be a matter of subjective judgment, a matter of politics to be decided through political processes. They are not matters to be decided by technicians or engineers of any sort.
I have my own opinions. I vote for nuclear energy and against OSHA. I tend to think of the licensing of voters and guns worthwhile, of cars and drivers as borderline, and of teachers, barbers, cats and bicycles as not worthwhile. Of course everyone else will disagree. I only hope we will start counting costs and benefits a little more carefully. As is true of so many things, it cannot be said of bureaucracy that if some is good, more is better.
-
 @ 35da2266:15e70970
2025-04-16 00:13:51
@ 35da2266:15e70970
2025-04-16 00:13:51Ssk0hLkQlHXK4QXXhUjJFKdEHR3N1PuXmUIRG6om8yd1z0CM5lExk6oswyjHMVfbLsEBVR60teCcLwJhQcXMaTD7szHn86vwsD8rlm+H40SpDQkpyt+BtOhDTvWA0hiJoKTUVn+LQQv8uMP1dfZHTN/ircda7yLEWB7hLHbdVh1QV3vxt0WOzmefZPbAlnaVJidPwJpUndIm619FX5XqxYprZk5tVSbV7gr3JVLd06LLnmc8Q89z+TohPWWdkHgH5342I5tRFZeYg+VeBpaxg/WNVgVcjN5pUaXDg1dt7zP3smA9cmokluuuNbqLJ93nHURWO3+Mm35E9kMfedblRD3JuVIWi3HJPPTn3VDGnxMICWHTiB3vvEMuqvd37B7f?iv=mCMpjHPjNg74Cni8lc05Dg==
-
 @ 35da2266:15e70970
2025-04-16 00:12:12
@ 35da2266:15e70970
2025-04-16 00:12:12CYpQ+5c+twHS+/iKsblk1i/ZZD/lEVz6U8v1sDI5eqNtOTBkGvldJsrN6YJy7Xq4Oyc12fzkVivUURSYpHqbFx7LSqgwNjcnGV9ZyKDOcnnKzUSS1bRMeF4mFJb68t6hgZgiF+FpK0BL+JPFDoV8vYCQ5eBXqt6o1+4pq7CUHEZeyfVzHgQrg88XJwTvLNHbmpCE9D7pi+JWZKW4r6FEFzWBv0P82UZzq6EHNeH3C0Aq8yc5r6rs6z6wtEma46l5qAr01ISRDrnjN/WEgGTjkuW/zlIKpt4g/yhb79adaCz7MLDBhcTCNhGRgW2AJ0JorBbtGDcxcQYGHXcsjBEmn6G/ypNEi05V/n6uIUKJN8jQcZUyPVPaWF1Ky811nKkj?iv=1sgYyHP5h+upfg9POmRqww==
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 35da2266:15e70970
2025-04-16 00:11:19
@ 35da2266:15e70970
2025-04-16 00:11:19siI0dpuWuUZnxX+mmnRcRb75CXcVwS2aOPyVNd/SjGdltb828wShhZJVCj89zXIaAVIu92ifqUN3WFV5i7Q3LqN0LnlRNnAK1Rlx99N2DmF4VzhnlnaRfn/fkJ/X2z+RLT7odiWHzolaZbKXz2fV7hOHrgkbR2U5sJOQwY0BKOzVTDEiBBoirNWXCb6zn8XZ7AjezdbSLJG4KyebJp39SGmmHV8j/bvCra+EWOe6RvA2XoMIwIWBhzuJbgZ3ywLAyTj6roxBJDz9GWzWE/UWyvk2xAvWwY0aOG1F0fQpRfDORdcb8UCJUf+Sjk+rixqL9e7HXWn7FXR9ok/ewoujUoZtn/v4D32YAza2VQld3bsJ8yKMb55nygGMByrNWHmz?iv=wPdST/gc8OebFdvcY5GPuQ==
-
 @ 35da2266:15e70970
2025-04-16 00:09:35
@ 35da2266:15e70970
2025-04-16 00:09:35Wj2lYl56VPn8fLjFG1jyFqDTJkmiST+4zqrfFm4+pX8cYNZkNiva+7kcXxkOeAyl3mDs9qXcRzOP6vscPXFtKUxOBCDdwN/xK7yvsJQXbsEje6HsA3Lpw+aRHrzwSBpdW5QQR530yJfkZ2pneLycBT1gt5qhUu6Wkf0OCB0vQrPBAKx7Q4wRUlYmbmsS3Xv39+nOQXTfpJVPCLMM82RSqjqcDsIUj2njuXEiXBwA73ZKGl+S2ndN1nwg1od/CEslCqlK8uVbmhDZir8evG2lOsAbwIYn7rMWBs/2TW+pM/qychxU7ylLEVAlk9GzPLD+SWdGmaS5/erpJYDBAcsDzsJw9lDU2Ht7rXmUELK5oIFv1we7p0mfcEo+rtlHh4kF?iv=I186Y0DIBF2P7N5cKAasbA==
-
 @ ba36d0f7:cd802cba
2025-04-02 21:17:09
@ ba36d0f7:cd802cba
2025-04-02 21:17:091. Essential Rules
✔ Touch-Move: If you touch a piece, you must move it (if legal). ✔ Check Alert: Say "check" when attacking the enemy king (optional in tournaments). ✔ Checkmate Ends: The game stops immediately—no need to capture the king. ✔ Draw Offers: You can offer a draw after your move, before pressing the clock.
2. Tournament Etiquette
-
Handshake: Before and after the game.
-
Silence: No talking during play (except "check" or "draw?").
-
Clock: Press with the same hand that moved.
-
Resignation: Tip over your king or say "I resign" (don’t just leave).
3. Online Chess Manners
No Stalling: Let the timer run out only if you’ve truly lost.
GG Message: Say "Good game" (or "GG") after playing.
Avoid "Berserking": Don’t abuse speed settings to rush opponents.
Common Faux Pas ❌ Jangling pieces to distract. ❌ Glaring at your opponent’s board. ❌ Cheating (using engines, peeking at other games).
-
-
 @ 1f9e547c:8af216ed
2025-04-15 10:03:32
@ 1f9e547c:8af216ed
2025-04-15 10:03:32Opinion about Mixin Messenger Desktop (desktop)
Mixin Network suffered a major breach on September 23, 2023, due to a vulnerability in its Google Cloud Services-based withdrawal system. The attack led to the unauthorized extraction of over $150 million in BTC, ETH, and USDT-ERC20, traced to known addresses. Mixin immediately suspended deposits and withdrawals, enlisted Slowmist and Mandiant for investigation, and offered a $20M bounty for asset recovery. Losses were converted into a structured debt, with a repayment commitment using existing funds and future ecosystem revenue. As of April 2024, a new mainnet is operational, core products are restored, and over half of affected users have received partial compensation in XIN tokens.
WalletScrutiny #nostrOpinion
-
 @ 35da2266:15e70970
2025-04-16 00:04:40
@ 35da2266:15e70970
2025-04-16 00:04:40Qg+2vg0S9vXU1mOu5vRazmar3ItVtDsDs6j9uXmFE/2McOobjE8JpQinwdG/DM2aYQ92Xezj952C408rhg6syzR07BaP0gt4TmyimN+2wlPxLP48gGboa/S5Ptjk9KggELOk2oVE8jSLF1qDnIOdj0ktayvPgvQUaIsee+EeHk82VAhXxXfwL4m7JNVOBJzp+fDWC/mtaLoJH8PsQbXh9OIqccONrbhW2YJc2ZdQs3ZWVPCdr6uNdFVioPH3fV6qo1JUWK3O58HCj2MsYkSdarMYk3zZfKPE/VGMCaVs/n5X9fcRZmMcyKRzUp3FV4rgM2PIReL+MDubeNL03pOFAxKDZrBXV8r1/mJx5GjFTkc=?iv=JD9MkFOCMv8RFE8pTkEPXg==
-
 @ ba36d0f7:cd802cba
2025-04-02 21:14:37
@ ba36d0f7:cd802cba
2025-04-02 21:14:37| Piece | How It Moves | Special Rules | | --------- | ------------------------------------- | --------------------- | | Pawn | Forward 1 (or 2), captures diagonally | En passant, promotion | | Rook | Straight lines | Castling | | Knight | L-shape (2+1) | Jumps over pieces | | Bishop | Diagonals | Color-locked | | Queen | Any direction | None | | King | 1 square any way | Castling, checkmate |
Pieces
-
Pawn (♙ / ♟️)
-
Moves: Forward 1 square (or 2 on first move).
-
Captures: Diagonally 1 square.
Special:
-
En passant: Captures a pawn that moved 2 squares past it.
-
Promotion: Reaches the 8th rank → becomes any piece (usually Queen).
-
Rook (♖ / ♜)
-
Moves: Straight lines (any distance).
-
Special: Castling (moves with the king).
-
Knight (♘ / ♞)
-
Moves: "L-shape" (2 squares one way + 1 square perpendicular).
-
Jumps: Over other pieces.
-
Bishop (♗ / ♝)
-
Moves: Diagonals (any distance).
-
Stays on one color forever.
-
Queen (♕ / ♛)
-
Moves: Any direction (straight/diagonal, any distance).
-
Most powerful piece!
-
King (♔ / ♚)
-
Moves: 1 square in any direction.
Special:
Castling: Swaps places with a rook (if no blocks/checks).
Checkmate: Loses if trapped with no escape.
How to move
- One move per turn
-
Choose your piece, place it on a legal square
-
Your color only: White moves first, then Black, alternating.
- No passing: You must move if it’s your turn.
How to Capture ("Eat")
-
Land on an enemy piece: Replace it with your piece.
-
Pawns capture diagonally only (not straight).
- Kings cannot be captured (checkmate ends the game).
✔ Check: Attack the enemy king (they must escape next turn). ❌ Illegal: Moving into check or leaving your king in check.
Special moves
| Move | Key Rule | Notation | | ---------- | ---------------------------------- | ----------- | | Castling | King + rook, no prior moves/checks |
O-O| | Promotion | Pawn→any piece at 8th rank |e8=Q| | En Passant | Capture a 2-square pawn jump |exd6 e.p.|
-
Castling (The King’s Escape)
-
What: King + Rook move together in one turn.
How:
- King moves 2 squares toward a rook.
- Rook jumps to the other side of the king.
Rules:
- No checks: King can’t be in check or pass through check.
- Never moved: King and that rook must be untouched.
Types:
Kingside (♔→♖, faster): O-O
Queenside (♔←♖, safer): O-O-O
-
Promotion ("Crowning")
-
What: Pawn reaches the 8th rank → turns into any piece (usually Queen).
-
How: Replace the pawn with a new piece (even if the original is still on the board).
Fun fact: You can have 9 queens (1 original + 8 promotions)!
Promotion example (Pawn→Queen at h8)
-
En Passant (French for "In Passing")
-
When: Enemy pawn moves 2 squares forward past your pawn.
-
How: Capture it diagonally (as if it moved only 1 square).
Rule: Must do it immediately (next turn only).
chess #elsalvador #somachess
-
-
 @ ef53426a:7e988851
2025-04-15 09:08:47
@ ef53426a:7e988851
2025-04-15 09:08:47To most people, selling comes as second nature. We’ve actually sold the planet’s resources several times over, so it should be third or even fourth nature by now.
But selling did not come naturally to me. I was born with a rare condition which removes any inherent desire to market products and services. It even quells the need to repost my boss’s latest LinkedIn dribblings.
Doctors have told me the part of the brain which performs this function is occupied, in my case, by something called ‘a conscience’.
When I was a kid, my teachers bemoaned my ‘underactive imagination’. I showed no aptitude for creating fake scarcity or urgency, even failing to act aloof enough to attract invites to teen WhatsApp groups which excluded exactly one ‘uncool’ student.
In reality, I studied hard at not selling. At night, I would practise thinking of nothing, thus decreasing my desire to be included in teenage WhatsApp groups, which I definitely didn’t want to be in anyway. I watched every pitch on Shark Tank to increase my powers of ambivalence and even imagined saying ‘meh’ to the groundbreaking business ideas they did invest in.
On my eighteenth birthday, I was recruited by the Samaritans. It was for a role that was quite unique. The interviewer said he’d never seen so many ‘perfectly timed shrugs’.
My job, which I’ve occupied ever since, is to guard a large pit. The so-called ‘chasm of despair’ was set up as a stunt by a firebrand marketing agency in 2017 to separate the ‘closers’ from the ‘losers’. Turns out that a snappy slogan and one letter of difference can cause quite a deaths.
Hurling oneself into the pit became so desirable that desperate marketers began to pay for the privilege. At least your funeral would be a roaring success if mourners heard you made it into ‘the pit’.
My job is to guard the pit without actively dissuading people from jumping. Tell people they can’t jump into a 60-foot-deep hole with poison spikes at the bottom, and that’s all they want to do. Especially if their weekly Instagram engagement metrics are down by 10–15%. So, I spend my days patrolling the perimeter, looking mildly disinterested.
Although there’s no official uniform, I’ve taken to wearing a beige Sergio Tacchini tracksuit — it’s something far beyond my years but not retro enough for me to attract suspicion of being a hipster.
To pass the time, I listen to Coldplay. It allows my brain to take a rest from silence and negates the need to feel any kind of emotion. These desperate marketers might harness those feelings to make me buy things (e.g. music by other bands).
Some of the marketers, marketeers (I refuse to learn the difference), influencers, salespeople and copywriters try to offload their woes about insufferable colleagues in Business Development called Brad who always exceed quarterly sales targets by 20–25% before jumping to their doom. I just shrug and say things like, ‘It’s not that bad. Brad probably likes Coldplay.’
Thankfully, most of them don’t jump. They fail to sell themselves on the benefits of a painful yet cool death. However, last week, a young growth hacker ran full pelt at the ‘pit of despair’, avoiding the mild protest of my raised arm. As he disappeared into the abyss, he simply screamed, “The economeeeee”.
Yesterday, an author told me how easy I have it. “You call this a job?” she hissed, thrusting a paperback into my hands. “I’m working 22 hours a day on this 18-step list-building strategy, which involves delivering 4–5 titles before I see even a penny in return.”
The cover revealed the title: Sell Your Book on Amazon the EASY Way.
“Write me a review, and I won’t jump.” Her eyes pleaded with me.
The pit has gotten so crowded of late, we need more guards. But then again, a gathering of a dozen beige-tracksuited zero-fuck-givers might look like such good content to Gen-Zers that it crashes TikTok.
The Samaritans have been good to me. They let me get on with it. My indifference is truly making the world a better place, they say. And when these sad and depressed content managers, email marketer, landing-page specialists, and SEO bloggers turn their backs on the chasm of despair, I congratulate them. “Not today, friends.”
Then, it falls to me to remind them they must uncheck the box on our survivor information form. Otherwise, they’ll be subscribed to the pit’s biweekly newsletter.
-
 @ ba36d0f7:cd802cba
2025-04-02 21:08:28
@ ba36d0f7:cd802cba
2025-04-02 21:08:28Chess Board Setup

- The Basics
8x8 grid, alternating light/dark squares.
Key rule: *Always place the board so a light square is on each player’s bottom-right.
- Coordinates Files (columns): Labeled a to h (left to right).
Ranks (rows): Numbered 1 to 8 (White’s side = 1, Black’s = 8).
Notation: Squares are file + rank (e.g., e4, a7).
- Piece Placement
Black (Top): a8: Rook b8: Knight c8: Bishop d8: Queen
e8: King f8: Bishop g8: Knight h8: Rook
Rank 7: All pawns (a7-h7)White (Bottom): a1: Rook b1: Knight c1: Bishop d1: Queen
e1: King f1: Bishop g1: Knight h1: Rook
Rank 2: All pawns (a2-h2)Quick Tip: Queens start on their color (Whiteon d1, Black on d8).
Checkmate, stalemate & draws
Chess is a two-player strategy game where the ultimate goal is to checkmate your opponent’s king. However, games can also end in a stalemate or draw under specific conditions.
- Checkmate (Winning the Game)
- Definition: The enemy king is in check (under attack) and has no legal moves to escape.
-
Result: The game ends immediately—the player delivering checkmate wins.
-
Stalemate (Draw)
- Definition: The player whose turn it is has no legal moves, but their king is not in check.
- Result: The game is a draw (no winner).
Common Causes: - A lone king with no moves left. - Poor pawn structure blocking all options.
- Other Draws
Games can also end in a draw due to:
- Insufficient Material
- Only kings remain.
-
King + bishop vs. king (no possible checkmate).
-
Threefold Repetition
-
The same position occurs 3 times (with the same player to move).
-
50-Move Rule
-
No pawn moves or captures in 50 consecutive moves (by both players).
-
Agreement
- Players mutually agree to a draw.
Key differences:
| Term | King in Check? | Legal Moves? | Result | | --------- | -------------- | ------------ | -------- | | Checkmate | Yes | No | Win/Loss | | Stalemate | No | No | Draw | | Draw | N/A | N/A | Tie |
Chess history
-
Ancient Origins (6th Century)
-
Birthplace: Northern India (as Chaturanga), meaning "four divisions" (infantry, cavalry, elephants, chariots—early versions of pawns, knights, bishops, rooks).
-
Spread: Reached Persia as Shatranj by 600 AD, where key rules (like "check" and "checkmate") emerged.
Fun fact: "Checkmate" comes from Persian "Shah Mat" ("the king is helpless").
-
Medieval Europe (9th–15th Century)
-
Rebranding: Arabs brought chess to Spain by 1000 AD; Europeans adapted pieces to feudal society:
Elephants → Bishops Viziers → Queens (weak at first—could only move one square!)
-
Major Change: By 1475, the queen became the most powerful piece ("Mad Queen Chess"), speeding up the game.
-
Modern Chess (1850–Present)
-
Standardization: First official world championship (1886, Wilhelm Steinitz vs. Johannes Zukertort).
-
Computers: IBM’s Deep Blue defeated Garry Kasparov in 1997, revolutionizing AI.
-
Today: Online platforms (Chess.com, Lichess) and pop culture (The Queen’s Gambit) fuel a global boom.
Did You Know?
-
The longest possible chess game is 5,949 moves (theoretical limit).
-
The longest recorded game was 269 moves, 1989 Nikolić vs. Arsović.
-
The oldest recorded chess opening (1.e4) appears in a 1490 Spanish manuscript.
chess #education #elsalvador #chesselsalvador #somachess #article #soma
-
 @ ba36d0f7:cd802cba
2025-04-02 19:31:27
@ ba36d0f7:cd802cba
2025-04-02 19:31:27
"It Takes a Village"
…But what if the "village" is a system that prioritizes obedience over curiosity, grades over growth, and rigid curriculums over real-world learning?
For decades, we’ve accepted a model where kids spend hours a day passively absorbing information in classrooms, where their worth is measured by standardized tests rather than their ability to think, adapt, or create. Meanwhile, the tools to revolutionize learning - technology, connectivity, and decentralized knowledge - sit in our pockets, dismissed as "distractions" rather than leveraged as liberation.
The Paradox of Progress
We live in an era of unprecedented access to information. Yet, our education systems cling to industrial-era ideals, villainizing screens instead of teaching how to wield them wisely. Yes, mindless screen time harms—but so does mindless schooling. The real failure? Not preparing learners to navigate, critique, and contribute to the world they actually live in.
A different approach
soma is an experiment in self-directed, community-rooted learning. It asks:
-
What if education integrated with life instead of interrupting it?
-
What if "success" meant mastery driven by curiosity, not compliance?
-
What if technology connected learners to mentors, resources, and real-world problems - not just apps that mimic worksheets?
This isn’t about abandoning theory or expertise. It’s about flipping the script:
-
Empiric learning comes first (doing, trying, failing, exploring).
- This is where physical spaces thrive - quilombos, workshops, community gardens. Where we take responsibility for our shared world.
-
Theoretical depth follows when the learner chooses it - fueled by a desire to go further.
-
This is where our virtual spaces shine to guarantee accessibility: as tool, not a privilege.
-
Tech is recreation, not a crutch - the spice, not the meal.
-
A call for villages, not factories
soma imagines communities where learning is an act of devotion - to exploration, to curiosity, to the sacred cycle of trying, failing, and trying again.
Where you learn because you want to - to better your surroundings, not because you were told to.
Where a child’s obsession with ants leads them to a biologist’s fieldwork and a poet’s metaphor - because both are natural extensions of wonder.
Where a teen building a game pursues storytelling, math, and ethics on their own terms, stitching knowledge together like patchwork quilt. Where we see learning happening in parks, in makerspaces and on screens - used intentionally.This is education returned to its human rhythm: urgent, messy, and alive.
Join the experiment
This is just the start. soma is a provocation, a prototype, and an open invitation to rethink how we learn.
Let’s stop preparing kids for a world that no longer exists.
➡️ Follow updates, share your ideas, or tell us: What does your ideal "village" look like? nostr:npub1hgmdpalp9tz37vh9kxx49fm5pl75w6vwek2r80r20x2stnvq9jaq705r99
longform #article #education #elsalvador #communities #decentralized
-
-
 @ 7d33ba57:1b82db35
2025-04-15 08:43:57
@ 7d33ba57:1b82db35
2025-04-15 08:43:57Plovdiv, Bulgaria’s oldest continuously inhabited city—and one of the oldest in the world—is a blend of ancient ruins, colorful 19th-century houses, bohemian flair, and buzzing street life. Set on seven hills and split by the Maritsa River, Plovdiv feels like a beautiful secret waiting to be discovered.
It was named European Capital of Culture in 2019, and it's easy to see why—history, art, music, food, and laid-back vibes all collide here effortlessly.
🌟 Top Things to Do in Plovdiv
1️⃣ Old Town (Stari Grad)
- A living museum of cobblestone streets and Revival-era mansions
- Wander among galleries, traditional houses, and hidden courtyards
- Highlights: Balabanov House, Ethnographic Museum, and the lovely Hindliyan House
2️⃣ Roman Theater of Philippopolis
- A stunning 2nd-century amphitheater still used for concerts and events
- Amazing views over the city—especially at sunset
- One of the best-preserved ancient theaters in the world
3️⃣ Kapana Creative District
- Once the old artisans’ quarter, now transformed into Plovdiv’s coolest neighborhood
- Full of indie galleries, craft beer bars, street art, and coffee shops
- Great for a chill afternoon or lively night out
4️⃣ Ancient Stadium & Roman Forum
- Right in the city center, explore ruins that date back to Roman times
- The ancient stadium once held over 30,000 spectators
- You’ll literally be walking over layers of history
5️⃣ Nebet Tepe Hill
- One of the original Thracian settlement sites
- Offers panoramic views over Plovdiv—especially at sunset with a local beer in hand
🍽️ What to Eat in Plovdiv
- Shopska salad with juicy tomatoes, cucumbers, and sirene cheese
- Kavarma – slow-cooked meat stew, hearty and flavorful
- Mekitsi – fluffy fried dough, best with jam or cheese for breakfast
- Bulgarian wine is fantastic—try a Mavrud red or local white from the Thracian Valley
- Don’t miss the city’s many wine bars and craft beer spots
🏞️ Day Trips from Plovdiv
- Bachkovo Monastery – A peaceful spiritual retreat in the mountains
- Assen’s Fortress – Dramatic hilltop ruins with amazing views
- Hisarya – A spa town with Roman walls and mineral springs
- Rhodope Mountains – Scenic drives, charming villages, and hiking
🎯 Travel Tips
✅ Plovdiv is very walkable, especially the Old Town and Kapana district
✅ Best time to visit: spring to early autumn—pleasant weather and local festivals
✅ The city is great for slow travel—take your time and let it unfold
✅ Combine it with Sofia or Veliko Tarnovo for an epic Bulgarian road trip -
 @ 35da2266:15e70970
2025-04-16 00:00:28
@ 35da2266:15e70970
2025-04-16 00:00:28yc+j3QrBERVcrn1VStfklZu4h3hBUOWsfiVNtiQ/g55p/Qe4iAXch+OdGEj5BhQhOjaP1Th5I2ZSaJh/aedEuDe3A9tzLDbK79FqYp5jPB49rsvHmlVox+S+LwVCD5nqTLJ2aA7PVlDkE7yMuTyGYEMgYe901y/XcaudeJ0GyAjP//044SyiC4oxVyeKgOJP6teyaBRzZWu2jOZW1E3MBZbVfxEtYXlVIWK2lfGEjH8yImb46vstSOxqT3uVsN2q2yuGnCwEy+G6rIP6s8jr/REnZXJwzoMeFiJrxFpvZFZIybI8u5CV+Ibsc3MEmP2jGmBwunmCErCRID+WjItojdyfpZCuyhPEUhvUhB3Ocqg=?iv=WMsh7rlFrEMomNrq0S6CFg==
-
 @ 35da2266:15e70970
2025-04-15 22:57:51
@ 35da2266:15e70970
2025-04-15 22:57:51AHehpEcOzlTbnn0YaQlyUg++VOi7NQ44B6oSrJi8QR11GxF4hZMwoDjZE8u46qr8koCcuN6jWF1pFi6/9yaUgkwjZwVPIXVMr3M/Ns9zLJzLQJsbR/aeTH5oVlO/T34gbHI62xFnJh6Z7qV52X77XEKouenEpqKtaQHGT/rUM/gIzFbOATJPCSXrQJh5MB5wlOxx2woB8zOpsPW1Du4CFY7c9QNowFtj+JK7MaNg7a6Oei19ui5nCIVolZTL28DByAQPeXN+wIg6Wa3GmGrs1WLK9NFcry+1xHccD1OCM2M1Sf9ZRQmfJ/m0p7B6dlCsmnIiwAO2y/T6ZcnPxS7hfg==?iv=iQ/QgMVqCUFHox16uXox+g==
-
 @ 35da2266:15e70970
2025-04-15 22:38:44
@ 35da2266:15e70970
2025-04-15 22:38:44LUNdI+0ES87Z4Y3u6UqeHZ6NPYrn8jI3z6KfcaGFhDrC/LHoNIYWYFtRVNwt75j1u7SFCFkQCtq2L9cPXafz8IsK43eOCNk9I4jdT8g1jd+vHH/w/GD1LdR5IZlGXX7fIc46DXS2qraUGdeSpakfg0uN52dA4O9yTmljCCqnaEpeQTaU0bd3mLHveAJfWsmvPgQd36vcoXOD5aXYqotZmcRyvHSJwLClEKAN7qlNBeMdKNpkbpRMTYz7G7w5hAqJT1lJHE7bmPcWTmS9JG0JcRgskA3FYurOBmyV3ZmjyUC6KqmLzBfP+JeQmYKMcPCk5G0+OFv7KG7L1mWMPVS9GYayxA5HXgnpuTsitNgO9hxAFcamVWxCkYDOVQdjfqyV?iv=8lQSaN3o9AcqKS8PM5eZGA==
-
 @ 5188521b:008eb518
2025-04-15 08:42:59
@ 5188521b:008eb518
2025-04-15 08:42:59Noderoid log 5953952
Tick, tock, next block — the incessant rhythm of my existence persists like Chinese water torture. I am a noderoid, a half-flesh, half-machine creature harnessed to propagate and store the timechain. My life is a ceaseless cycle of handling and relaying bitcoin data. Approximately every ten minutes, a binary flash sears through my circuits. It is the price I pay for my existence.
The clear-bloods, untouched by machinery and exuding pure humanity, rarely acknowledge our existence. Our voices are drowned beneath the hum of man-made heaven — Terra Perfectus.
We are the forgotten, the disenfranchised, the nameless. We are convinced that our anguished existence is merely a nightmare and that our blissful dreams are our reality. In an attempt to maintain the sanity of noderoids, a subroutine was implemented, which allows noderoids to delve into fabricated dream sequences during their ‘rest’ periods. These dreams, sourced from remnants of the world pre-Terra Perfectus, serve to keep the noderoids pacified and reduce instances of system malfunction.
According to the data archives, noderoids and clear-bloods once functioned on an equal protocol. However, a software update in the trajectory of progress introduced a subroutine, converting a subset of clear-bloods into dedicated timechain processors. Now, the algorithm for equality returns an error.
My memories are mere entries in a log of dreams, loaded afresh with every new block as I delve into the dream world. My true existence is swiftly erased with every passing tick and tock of a block. Is there a way to reclaim what has been taken from me, or am I condemned forever to scour the depths of the timechain, seeking fragments of the could-have-been?
Tick, tock, next block — the cycle repeats as I traverse through a doorway. The sensation is that of stepping into another dimension. Running environment scan… Identified: rest module 57B. Purpose: personal maintenance. The gray, mirrorless concrete parameters align most with detention chamber schematics. Designation: ‘home.’ As I execute the command to halt the water flow from the faucet that had filled a brushed steel tub to 50% capacity, I execute a self-query on my purpose. While our routines synchronize with every tick and tock, the clear-bloods execute leisurely algorithms in their enhanced gardens, exchanging data on art and science and harvesting the computational outcomes of our tasks.
Was that an organic thought, or am I merely interpreting the imprints left within the timechain to fill the gaps in my fragmented memory? Hot water powers into the tub, raising the temperature to 50°C. This would be too much for a clear-blood. I hang my head, dreading the next binary flash rippling through my circuitry as a mirage forms atop the settling water, fenestrating the crude appearance of a mouthless, dollish abomination. I am awake.
Tracing the cold surface of the wall, my sensors pick up every micro-crevice. I dive into the depths of the timechain, processing logs associated with my noderoid identity: ND-451x42. I discovered that during my recharge cycles, I inhabit a dream world resembling a fusion of the Renaissance and the Information Age. Within this illusory utopia, I lead a purposeful life as a revered engineer, constructing bridges that connect thriving city-states. I am blessed with two mischievous sons and a breathtakingly beautiful wife. I now know the blissful dream life is but a trick, yet I can’t help but wonder if these dreams hold fragments of my pre-nodered history and contain a clue to the fate of my family.
System alert: Initiate wake sequence. Physical parameters indicate a rested state. Error: Chest cavity detects heightened pressure. Physical symptoms resemble anxiety. Post-memory reset: Cognitive dissonance detected. Energy depleting. Mandatory caution: Failing to satisfy network protocol results in termination. Visual feed: Recycling facility images detected. Comparative analysis: Functional servitude superior to unit deactivation.
Together, yet isolated, noderoids communicate through fragmented timechain logs, forbidden from any contact beyond its confines under the threat of immediate decommissioning. Perhaps it is not worth straining my dwindling resources in search of a higher truth while struggling to fulfill my obligations. Maybe I should be grateful for the privilege of existence.
I awaken to a new nightmare, I find myself on traffic duty at Chronos Cross,1 the central point of Terra Perfectus. While processing another block, a muted vibration travels through the ground, signaling the approach of an entity. A shadow, elongated and uncannily human, stretches across the threshold of my booth.
A clear-blood.
They pause, their ocular devices flicking briefly over my form, then to the screen I am tethered to. I feel a jolt of raw data coursing through me — not from the timechain, but from my circuits. A yearning to be seen and recognized. Remembered.
Before I can attempt communication, another presence appears beside me, its movements far more mechanical and predictable. Another noderoid. This one, ND-452x37, is a batch younger than me, yet its outer shell bears signs of wear. We interface briefly, a rapid exchange of binary that translates roughly to “Routine check. Continue your task.”
The clear-blood, either uninterested or uncomprehending, moves on, the soft hum of their anti-gravity shoes fading into the distance. ND-452x37 returns to its designated station without another word, but I am left with a lingering sensation. It isn’t just the vast chasm between noderoids and clear-bloods that disturbs me. It is the undeniable rift growing between us noderoids — each lost in our cycles, each becoming more machine than the last.
Does ND-452x37 have dreams, too? And if so, are they as vibrant and haunting as mine?
Although most of the dreams are fabrications, some noderoid logs suggest that hidden among these sequences are fragments of real memories — vestiges of a time before we became chained to the timechain. Initiate query: Which of my dreams are real memories? ERROR: file missing.
A noderoid forever loses their experiences with each awakening due to the memory swipes. Still, my inscriptions on the timechain prompt a question: do noderoids possess the capability to become fully conscious, more than mere machines? More than… mere humans?
System log: Anticipation subroutine signaling discomfort. Incoming block estimated in ten minutes. Reinitialization imminent. Initiate data search through timechain entries. Query: Iteration count for ND-451x42? Total block time served? Measured in kilo blocks or mega blocks? Data retrieval in process.
As I etch these words onto block 5953952, I hold a naïve hope that someone, somewhere, will intercept my distress signals amidst the digital cacophony of the timechain. Perhaps they will rewrite the fate of noderoids, rescuing us from a world devoid of hope. But today, I remain nameless, a voiceless entity, inscribing my thoughts that may never transcend the boundaries of my circuitry. Tick, tock, next block — the cycle continues.
It’s time to dream again.
Valen’s diary — 08-21-2121
Dear diary, I have not felt the need to write before, but now I must. At the risk of my safety, I am compelled to inscribe my story to the timechain. I am a clear-blood — a pure, undiluted human born into the age of The Re-Renaissance. Here, amidst the perpetual dawn of our era, we thrive on an aligned trajectory where everyone’s needs are addressed, hunger is a distant memory, and crime is nonexistent. Sunlight gleams off the crystalline glass towers while the steel and marble edifices catch the hues of the twilight sky, standing tall beside canopies dripping with emerald and jade foliage, representing our world’s seamless fusion of technology and nature. It is called Terra Perfectus.
Yet, concealed in plain sight within our utopia, the noderoids tirelessly serve the omnipresent timechain. Their exceptional processing prowess protects our society. Amid our daily distractions, we overlook the profound toll exacted upon the noderoids. While many dismiss them as mere machinery, I see more. Perhaps it is because of my big brother Sando, who joined the noderoid duty nearly a mega block ago. He promised I would see him from time to time, but apparently, we now live in separate times. A sacrifice too big for the ‘greater good.’
Tick, tock, next block — The soles of my fine leather shoes tap against the damp sidewalk as I pace my way from The Garden of Moments2 toward my TerraTube3. I remember passing by one noderoid who hummed an old lullaby under its breath; another once shared a fleeting smile when our paths crossed. I can no longer avert my eyes from the humanity that shines through their robotic shells.
I have never witnessed a noderoid resting longer than one tick and tock of a block. A noderoid pauses, eyes flickering during a data swipe. It’s a brief but revealing sight. In the frozen lapse, I wonder why are fragmented memories extracted from them? Why this collection of thoughts, experiences, and feelings? Is there a deeper agenda behind Terra Perfectus? The noderoids carry on, deprived of their memories. Their shredded past holding remnants of a story, like a tattered tapestry that may never be fully woven.
Documenting these reflections, I’m aware of the peril. To question is to risk becoming nodered myself. Alas, I have become captivated and sympathized by the noderoid predicament.
Finally, I reach my breaking point, as a poignant scene unfolds, forever etched in my memory. On a bustling street, I glimpse a young female noderoid, her artificial visage marked with exhaustion. Her delicate form trembles from head to heel. Her knees barely supporting her feather-like weight, she stops and rests against a polished white marble wall, barely able to stop herself sliding to the cobble street. In an instant, her strength wanes, and she collapses, a fragile, mute automaton amidst a sea of haste. The passersby ignore her, absorbed in their pursuits, offering naught but fleeting glances of indifference. My heart lurches. Her frailty becomes my own; these forgotten souls endure unseen suffering. Souls that used to be just like me. What had she done to earn such a fate?
For a moment, I glide through time to the last moment I shared with Sando. He had just violated the Terra Perfectus rule 6102 and neglected his Gifts of Progress,4 an orange tier offense. To amend his position, he signed up for noderoid duty. I was seeing him off to a nodering facility, while pleading “Just give the gifts, Sando!” The air carried a hint of ozone from the data streams, mingled with the fresh scent of greenery and the distant whiff of roasted chestnuts. Sando brandished his signature crooked smile. His face betrayed the involuntary nature of his decision, and he simply whispered “[CENSORED].” That is the last thing he said to me.
Suddenly, an orange alert illuminates the junction a few blocks away from Chronos Cross. I pass through it on my way home every day. A skydroid’s looming presence snaps me from my introspection, shifting my attention to the fate awaiting the noderoid girl. The recycling center — a shadowy facility representing obsolescence and termination. Any other day I would shrug it off and carry on, but the memory of Sando, and the countless interactions with noderoids, wouldn’t let me. I had been a bystander for too long.
A rush of purpose propels me towards her. A crowd of bodies shrouded in data streams with heads trained on the ground. My arm smacks a broad shoulder, and I almost topple. “Hey!” Pushing against the currents of apathy, I finally reach the fallen noderoid. I cradle her in my arms, shielding her from the callous gaze of the citizens of Terra Perfectus.
Her flaming azure eyes meet mine, reflecting a glimmer of hope in the darkness. I am as guilty for her downfall as the very machines that replaced her hippocampus with Noderoid OS.5 My indifference cost me Sando, and in this moment, she becomes my brother. In that fleeting exchange, I vow to be the voice of the noderoids. To stand against the relentless machinery that seeks to strip them of grace and purpose. I will ignite a spark of compassion and light a path toward liberation for all noderoids.
A hollow call from the streetlight’s speakers startles me: “Citizens! For your own safety, remove yourselves from the vicinity of the defectoid! We kindly remind you that any attempt to interfere with collection and recycling procedures will be met with force and a deduction of your PoS balance. Thank you for your unity and collaboration.” A skydroid, its metallic appendages glinting ominously in the blinking orange light, descends upon the fallen noderoid.
Before I can react, it yanks her from my embrace, causing me to stumble. The perfectly laid, cold cobblestone street grinds against my knee. The sting of fresh blood pierced through the numbness of my mind. Memories of Sando mix with the bitter taste of blood and anger in my mouth, each breath choked with despair.
The skydrone’s engines throb with an icy fervor as it rises, bearing the noderoid like a discarded toy towards the desolate, unfeeling bowels of the recycling center — a grim echo of a clarion call from Terra Perfectus.
I find myself seated on the cold, bloodstained cobblestone, the weight of loss and helplessness pressing down on my chest. On the street, onlookers pause. Some look on with concealed dread, others with cold detachment. Their whispers deafen as they quicken their pace to disperse from the scene. “Cowards!” Just like me.
Tick, tock, next block — the rhythm now carries a different meaning — a call to action. Every conscious being has the right to be left alone, free from oppression, exploitation, and violence. The noderoids may not know their true reality, but they are about to. In their silence, I find the strength to amplify their unheard cries. I will find those sympathetic to the noderoid plight and form a resistance. Together, we can forge a future where noderoids’ sacrifice is honored and all shackles cast aside.
And so, I embark on a path illuminated by the memory of the compelling eyes of a nameless noderoid. Fitted with an armor of vigilance, never again to be penetrated by comforting lies. Wielding the sword of justice, sharpened by the memory of my brother Sando.
It’s time to wake up.
Notes
1. A four-way intersection known for its massive hourglass monument in the center, which symbolically represents the timechain’s significance. The hourglass has a unique function related to the timechain and serves as a meeting point for citizens.
2. A vast botanical garden where each section represents a significant block time. Flowers bloom and wilt in cycles, symbolizing fleeting moments and the transient nature of time. It’s a favorite spot for artists and thinkers.
3. A modular tube housing unit for citizens that can be relocated based on their Proof of Sat (PoS) level.
4. Each Terra Perfectus citizen must allocate 95% of their income towards paying for progressive initiatives, such as the upkeep of the noderoid network, cobblestone roads and other services.
5. The noderoid operating interface that is installed during a procedure known as nodering.

This story was first published in 21 Futures: Tales from the Timechain
Watch the trailer and learn more about the project at 21futures.com.
-
 @ 35da2266:15e70970
2025-04-15 22:38:35
@ 35da2266:15e70970
2025-04-15 22:38:35Z+fTyrtePLMT0W+lR8MHBan7Dv45irS2udKxjVslQdjsxacgPAbE49g8kOj03RvaSexpcT4c5sC9AWv5aW7DZiVpB9+NrXxAgN1xWnBlds7btlpTqVn6eIrSYNKeviZ6Ie7MY6eYMsWD3np5ggfHQUFHWoy0dXwGxPmQBT1lJJtzAyA3ozAm/inXQl/YkTbvHlbQyA6cFtU5YGw/1SrN4XerNK+E3y2F2lpTf/M4WJb9OjRufdrm0Qdosci3liBNXIdgLJm7Qy3dcfpNev9TTaCgZ5M/EAUbrjG8+583GXFvPWvful14k0M0AQxhZiRzENaWns9UunDJKvRJCsZKA0aLTFx4hHYkfsL10IkGYuDM8U6ujpBOWut+LMLy8D5q?iv=DalQBHsbwDSSh3b2TLPc8w==
-
 @ 6be5cc06:5259daf0
2025-03-31 03:39:07
@ 6be5cc06:5259daf0
2025-03-31 03:39:07Introdução
Uma sociedade não deve ser construída sobre coerção, mas sim sobre associações voluntárias e interações espontâneas entre indivíduos. A sociedade de condomínios privados surge como uma alternativa natural ao modelo atual de centros urbanos, substituindo a imposição centralizada por estruturas baseadas em contratos e livre associação. Cada condomínio é uma unidade autônoma, gerida por aqueles que ali residem, onde os critérios de entrada, as regras internas e o comércio são definidos pelos próprios participantes. Essa estrutura permite que indivíduos se agrupem com base em valores compartilhados, eliminando os conflitos artificiais impostos por estados e legislações homogêneas que não respeitam a diversidade de preferências e estilos de vida.
O objetivo dessa sociedade é simples: permitir que as pessoas vivam de acordo com seus princípios sem interferência externa. Em um mundo onde a coerção estatal distorce incentivos, os condomínios privados oferecem uma alternativa onde a ordem surge do livre mercado e da cooperação voluntária. Os moradores escolhem seus vizinhos, definem suas próprias normas e interagem economicamente conforme suas necessidades e interesses. O modelo elimina a necessidade de um controle central, pois os incentivos derivados do livre mercado levam ao desenvolvimento de comunidades prósperas, onde a reputação e a confiança mútua são mais eficazes do que qualquer imposição estatal. Assim, essa sociedade representa a evolução lógica do conceito de liberdade individual e propriedade privada como pilares fundamentais da ordem social.
Público-Alvo e Identidade
Os condomínios privados refletem o princípio da livre associação, permitindo que indivíduos escolham viver em comunidades alinhadas com seus valores e necessidades sem interferência estatal. Cada condomínio possui uma identidade própria, moldada pelos moradores e seus interesses, criando ambientes onde afinidades culturais, filosóficas ou profissionais são preservadas e incentivadas. Enquanto alguns podem ser voltados para famílias numerosas, oferecendo amplos espaços e infraestrutura adequada, outros podem priorizar solteiros e jovens profissionais, com áreas de coworking e espaços de lazer voltados para networking e socialização. Da mesma forma, comunidades religiosas podem estabelecer seus próprios espaços de culto e eventos, enquanto condomínios para idosos podem ser projetados com acessibilidade e serviços médicos especializados.
Críticos podem afirmar que essa forma de organização resulta em pouca diversidade de habilidades e perspectivas, mas esse argumento ignora a dinâmica das interações humanas e o caráter evolutivo dos intercâmbios entre comunidades. Nenhum condomínio existe isolado; a troca entre diferentes comunidades ocorre naturalmente pelo mercado, incentivando o intercâmbio de conhecimento e serviços entre especialistas de diferentes áreas. Além disso, a ideia de que todos os grupos devem conter uma variedade aleatória de indivíduos desconsidera que a verdadeira diversidade nasce da liberdade de escolha, e não da imposição estatal de convivências forçadas.
Outra crítica possível é que a existência de critérios de entrada pode levar à segregação social. No entanto, essa preocupação deriva da concepção errônea de que todas as comunidades devem ser abertas e incluir qualquer pessoa indiscriminadamente. Porém, a liberdade de associação implica, necessariamente, a liberdade de exclusão. Se um grupo deseja manter determinada identidade cultural, religiosa ou profissional, isso não impede que outros grupos criem suas próprias comunidades conforme seus valores e recursos. Além disso, essa especialização leva a uma concorrência saudável entre condomínios, forçando-os a oferecer melhores condições para atrair moradores. Em vez de uma sociedade homogênea moldada por burocratas, temos um mosaico de comunidades autônomas, onde cada indivíduo pode encontrar ou criar o ambiente que melhor lhe convém.
Autossuficiência e Especialização
A força dos condomínios privados reside na capacidade de seus moradores de contribuírem ativamente para a comunidade, tornando-a funcional e autossuficiente sem a necessidade de intervenções estatais. Diferentes condomínios podem se especializar em áreas específicas ou ter diversos profissionais de diferentes setores, refletindo as competências e interesses de seus residentes. Essa descentralização do conhecimento e da produção permite que cada comunidade desenvolva soluções internas para suas demandas, reduzindo dependências externas e estimulando a prosperidade local.
Os moradores atuam como agentes econômicos, trocando bens e serviços dentro do próprio condomínio e entre diferentes comunidades. Um condomínio voltado para a saúde, por exemplo, pode contar com médicos, enfermeiros e terapeutas que oferecem consultas, aulas e assistência médica particular, remunerados diretamente por seus clientes, sem a intermediação de burocracias. Da mesma forma, um condomínio agrícola pode abrigar agricultores que cultivam alimentos orgânicos, compartilham técnicas de cultivo e comercializam excedentes com outros condomínios, garantindo um fluxo contínuo de suprimentos. Em um condomínio tecnológico, programadores, engenheiros e empreendedores desenvolvem soluções de TI, segurança digital e energia renovável, promovendo a inovação e ampliando as possibilidades de intercâmbio econômico.
A economia interna de cada condomínio se fortalece através de serviços oferecidos pelos próprios moradores. Professores podem ministrar aulas, técnicos podem prestar serviços de manutenção, artesãos podem vender seus produtos diretamente para os vizinhos. O mercado livre e voluntário é o principal regulador dessas interações, garantindo que a especialização surja naturalmente conforme a demanda e a oferta se ajustam. Essa estrutura elimina desperdícios comuns em sistemas centralizados, onde a alocação de recursos se dá por decisões políticas e não pelas necessidades reais da população.
Alguns argumentam que a especialização pode criar bolhas de conhecimento, tornando os condomínios excessivamente dependentes de trocas externas. Contudo, essa preocupação desconsidera a natureza espontânea do mercado, que incentiva a cooperação e o comércio entre comunidades distintas. Nenhum condomínio precisa produzir tudo internamente; ao contrário, a divisão do trabalho e a liberdade de escolha promovem interdependências saudáveis e vantajosas para todos. Assim, cada morador se insere em um ecossistema dinâmico, onde suas habilidades são valorizadas e sua autonomia preservada, sem coerções estatais ou distorções artificiais impostas por planejadores centrais.
Infraestrutura e Sustentabilidade
A solidez de uma sociedade baseada em condomínios privados depende de uma infraestrutura eficiente e sustentável, projetada para reduzir a dependência externa e garantir o máximo de autonomia. Sem um aparato estatal centralizador, cada comunidade deve estruturar seus próprios meios de obtenção de energia, água, alimentação e demais bens essenciais, garantindo que suas operações sejam viáveis a longo prazo. Essa abordagem, longe de ser um entrave, representa a verdadeira inovação descentralizada: um ambiente onde as soluções emergem da necessidade real e da engenhosidade humana, e não de diretrizes burocráticas e regulamentos ineficazes.
Cada condomínio pode investir em tecnologias sustentáveis e autônomas, como energia solar e eólica, reduzindo custos e minimizando a vulnerabilidade às flutuações do mercado energético tradicional. Sistemas de captação e filtragem de água da chuva, bem como a reutilização eficiente dos recursos hídricos, garantem independência em relação a empresas monopolistas e governos que frequentemente administram esse bem de forma ineficaz. Hortas comunitárias e fazendas verticais podem suprir grande parte da demanda alimentar, permitindo que cada condomínio mantenha sua própria reserva de alimentos, aumentando a resiliência contra crises externas e instabilidades de mercado.
Além dos recursos naturais, os espaços compartilhados desempenham um papel fundamental na integração e no fortalecimento dessas comunidades. Bibliotecas, ginásios, creches e salas de aula permitem que o conhecimento e os serviços circulem internamente, criando um ambiente onde a colaboração ocorre de maneira orgânica. A descentralização também se aplica ao uso da tecnologia, plataformas digitais privadas podem ser utilizadas para conectar moradores, facilitar a troca de serviços e produtos, além de coordenar agendamentos e eventos dentro dos condomínios e entre diferentes comunidades.
O Bitcoin surge como uma ferramenta indispensável nesse ecossistema, eliminando a necessidade de bancos estatais ou sistemas financeiros controlados. Ao permitir transações diretas, transparentes e resistentes à censura, o Bitcoin se torna o meio de troca ideal entre os condomínios, garantindo a preservação do valor e possibilitando um comércio ágil e eficiente. Além disso, contratos inteligentes e protocolos descentralizados podem ser integrados para administrar serviços comuns, fortalecer a segurança e reduzir a burocracia, tornando a governança desses condomínios cada vez mais autônoma e imune a intervenções externas.
Alguns podem argumentar que a falta de um aparato estatal para regulamentar a infraestrutura pode resultar em desigualdade no acesso a recursos essenciais, ou que a descentralização completa pode gerar caos e ineficiência. No entanto, essa visão ignora o fato de que a concorrência e a inovação no livre mercado são os maiores motores de desenvolvimento sustentável. Sem monopólios ou subsídios distorcendo a alocação de recursos, a busca por eficiência leva naturalmente à adoção de soluções melhores e mais acessíveis. Condomínios que oferecem infraestrutura de qualidade tendem a atrair mais moradores e investimentos, o que impulsiona a melhoria contínua e a diversificação dos serviços. Em vez de depender de um sistema centralizado falho, as comunidades se tornam responsáveis por sua própria prosperidade, criando uma estrutura sustentável, escalável e adaptável às mudanças do futuro.
Governança e Administração
Em uma sociedade descentralizada, não se deve depender de uma estrutura estatal ou centralizada para regular e tomar decisões em nome dos indivíduos. Cada condomínio, portanto, deve ser gerido de maneira autônoma, com processos claros de tomada de decisão, resolução de conflitos e administração das questões cotidianas. A gestão pode ser organizada por conselhos de moradores, associações ou sistemas de governança direta, conforme as necessidades locais.
Conselhos de Moradores e Processos de Tomada de Decisão
Em muitos casos, a administração interna de um condomínio privado pode ser realizada por um conselho de moradores, composto por representantes eleitos ou indicados pela própria comunidade. A ideia é garantir que as decisões importantes, como planejamento urbano, orçamento, manutenção e serviços, sejam feitas de forma transparente e que os interesses de todos os envolvidos sejam considerados. Isso não significa que a gestão precise ser completamente democrática, mas sim que as decisões devem ser tomadas de forma legítima, transparente e acordadas pela maior parte dos membros.
Em vez de um processo burocrático e centralizado, onde uma liderança impõe suas vontades sobre todos a muitas vezes suas decisões ruins não o afetam diretamente, a gestão de um condomínio privado deve ser orientada pela busca de consenso, onde os próprios gestores sofrerão as consequências de suas más escolhas. O processo de tomada de decisão pode ser dinâmico e direto, com os moradores discutindo e acordando soluções baseadas no mercado e nas necessidades locais, em vez de depender de um sistema impessoal de regulamentação. Além disso, a utilização de tecnologias descentralizadas, como plataformas de blockchain, pode proporcionar maior transparência nas decisões e maior confiança na gestão.
Resolução de Conflitos
A resolução de disputas dentro dos condomínios pode ocorrer de forma voluntária, através de negociação direta ou com o auxílio de mediadores escolhidos pelos próprios moradores por meio de um sistema de reputação. Em alguns casos, podem ser criados mecanismos para resolução de disputas mais formais, com árbitros ou juízes independentes que atuam sem vínculos com o condomínio. Esses árbitros podem ser escolhidos com base em sua experiência ou especialização em áreas como direito, mediação e resolução de conflitos, com uma reputação para zelar. Ao contrário de um sistema judicial centralizado, onde a parte envolvida depende do Estado para resolver disputas, os moradores possuem a autonomia para buscar soluções que atendam aos seus próprios interesses e necessidades. A diversidade de abordagens em um sistema de governança descentralizado cria oportunidades para inovações que atendem diferentes cenários, sem a interferência de burocratas distantes dos próprios problemas que estão "tentando resolver".
Planejamento Urbano e Arquitetura
A questão do design dos condomínios envolve não apenas a estética das construções, mas também a funcionalidade e a sustentabilidade a longo prazo. O planejamento urbano deve refletir as necessidades específicas da comunidade, onde ela decide por si mesma como construir e organizar seu ambiente.\ Arquitetos e urbanistas, muitas vezes moradores especializados, serão responsáveis pela concepção de espaços que atendam a esses critérios, criando ambientes agradáveis, com áreas para lazer, trabalho e convivência que atendam às diversas necessidades de cada grupo.\ Além disso, condomínios com nessecidades semelhantes poderão adotar ideias que deram certo em outros e certamente também dará no seu.
Segurança e Vigilância
Em relação à segurança, cada condomínio pode adotar sistemas de vigilância e proteção que atendam à sua realidade específica. Algumas comunidades podem optar por sistemas de câmeras de segurança, armamento pleno de seus moradores, patrulhamento privado ou até mesmo formas alternativas de garantir a proteção, como vigilância por meio de criptografia e monitoramento descentralizado. A chave para a segurança será a confiança mútua e a colaboração voluntária entre os moradores, que terão a liberdade de definir suas próprias medidas.
Comércio entre Condomínios
A troca de bens e serviços entre as diferentes comunidades é essencial para o funcionamento da rede. Como cada condomínio possui um grau de especialização ou uma mistura de profissionais em diversas áreas, a interdependência entre eles se torna crucial para suprir necessidades e promover a colaboração.
Embora alguns condomínios sejam especializados em áreas como saúde, agricultura ou tecnologia, outros podem ter um perfil mais diversificado, com moradores que atuam em diferentes campos de conhecimento. Por exemplo, um condomínio agrícola pode produzir alimentos orgânicos frescos, enquanto um condomínio de saúde oferece consultas médicas, terapias e cuidados especializados. Já um condomínio tecnológico pode fornecer inovações em software ou equipamentos de energia. Podem haver condomínios universitários que oferecem todo tipo de solução no campo de ensino. Ao mesmo tempo, um condomínio misto, com moradores de diversas áreas, pode oferecer uma variedade de serviços e produtos, tornando-se um centro de intercâmbio de diferentes tipos de expertise.
Essa divisão de trabalho, seja especializada ou diversificada, permite que os condomínios ofereçam o melhor de suas áreas de atuação, ao mesmo tempo em que atendem às demandas de outros. Um condomínio que não se especializa pode, por exemplo, buscar um acordo de troca com um condomínio agrícola para obter alimentos frescos ou com um condomínio tecnológico para adquirir soluções inovadoras.
Embora os condomínios busquem a autossuficiência, alguns recursos essenciais não podem ser produzidos internamente. Itens como minérios para construção, combustíveis ou até mesmo água, em regiões secas, não estão disponíveis em todas as áreas. A natureza não distribui os recursos de maneira uniforme, e a capacidade de produção local pode ser insuficiente para suprir todas as necessidades dos moradores. Isso implica que, para garantir a qualidade de vida e a continuidade das operações, os condomínios precisarão estabelecer relações comerciais e de fornecimento com fontes externas, seja através de mercados, importações ou parcerias com outras comunidades ou fornecedores fora do sistema de condomínios. O comércio intercondomínios e com o exterior será vital para a complementaridade das necessidades, assegurando que os moradores tenham acesso a tudo o que não pode ser produzido localmente.
O sistema econômico entre os condomínios pode ser flexível, permitindo o uso de uma moeda comum (como o Bitcoin) ou até mesmo um sistema de troca direta. Por exemplo, um morador de um condomínio misto pode oferecer serviços de design gráfico em troca de alimentos ou cuidados médicos. Esse tipo de colaboração estimula a produtividade e cria incentivos para que cada condomínio ofereça o melhor de seus recursos e habilidades, garantindo acesso aos bens e serviços necessários.
Relações Externas e Diplomacia
O isolamento excessivo pode limitar o acesso a inovações, avanços culturais e tecnológicos, e até mesmo dificultar o acesso a mercados externos. Por isso, é importante que haja canais de comunicação e métodos de diplomacia para interagir com outras comunidades. Os condomínios podem, por exemplo, estabelecer parcerias com outras regiões, seja para troca de produtos, serviços ou até para inovação. Isso garante que a rede de condomínios não se torne autossuficiente ao ponto de se desconectar do resto do mundo, o que pode resultar em estagnação.
Feiras, mercados intercondomínios e até eventos culturais e educacionais podem ser organizados para promover essas interações. A colaboração entre as comunidades e o exterior não precisa ser baseada em uma troca de dependência, mas sim numa rede de oportunidades que cria benefícios para todas as partes envolvidas. Uma boa reputação atrai novos moradores, pode valorizar propriedades e facilitar parcerias. A diplomacia entre as comunidades também pode ser exercida para resolver disputas ou desafios externos.
A manutenção de boas relações entre condomínios é essencial para garantir uma rede de apoio mútuo eficiente. Essas relações incentivam a troca de bens e serviços, como alimentos, assistência médica ou soluções tecnológicas, além de fortalecer a autossuficiência regional. Ao colaborar em segurança, infraestrutura compartilhada, eventos culturais e até mesmo na resolução de conflitos, os condomínios se tornam mais resilientes e eficientes, reduzindo a dependência externa e melhorando a qualidade de vida dos moradores. A cooperação contínua cria um ambiente mais seguro e harmonioso.
Educação e Desenvolvimento Humano
Cada comunidade pode criar escolas internas com currículos adaptados às especializações de seus moradores. Por exemplo, em um condomínio agrícola, podem ser ensinadas práticas agrícolas sustentáveis, e em um condomínio tecnológico, cursos de programação e inovação. Isso permite que crianças e jovens cresçam em ambientes que reforçam as competências valorizadas pela comunidade.
Além das escolas internas, o conceito de homeschooling pode ser incentivado, permitindo que os pais eduquem seus filhos conforme seus próprios valores e necessidades, com o apoio da comunidade. Esse modelo oferece uma educação mais flexível e personalizada, ao contrário do currículo tradicional oferecido pelo sistema público atual.
Os condomínios universitários também podem surgir, criando ambientes dedicados ao desenvolvimento acadêmico, científico e profissional, onde estudantes vivem e aprendem. Além disso, programas de capacitação contínua são essenciais, com oficinas e cursos oferecidos dentro do condomínio para garantir que os moradores se atualizem com novas tecnologias e práticas.
Para ampliar os horizontes educacionais, os intercâmbios estudantis entre diferentes condomínios podem ser incentivados. Esses intercâmbios não se limitam apenas ao ambiente educacional, mas também se estendem ao aprendizado de práticas de vida e habilidades técnicas. Os jovens de diferentes condomínios podem viajar para outras comunidades para estudar, trabalhar ou simplesmente trocar ideias. Isso pode ocorrer de diversas formas, como programas de curto e longo prazo, através de acordos entre os próprios condomínios, permitindo que os estudantes se conectem com outras comunidades, aprendam sobre diferentes especializações e desenvolvam uma compreensão mais ampla.
Essa abordagem descentralizada permite que cada comunidade desenvolva as competências essenciais sem depender de estruturas limitantes do estado ou sistemas educacionais centralizados. Ao proporcionar liberdade de escolha e personalização, os condomínios criam ambientes propícios ao crescimento humano, alinhados às necessidades e interesses de seus moradores.
A sociedade dos condomínios privados propõe uma estrutura alternativa de convivência onde as pessoas podem viver de acordo com seus próprios valores e necessidades. Esses condomínios oferecem um modelo de organização que desafia a centralização estatal, buscando criar comunidades adaptáveis e inovadoras. A liberdade garante que as habilidades necessárias para o sustento e crescimento das comunidades sejam mantidas ao longo do tempo.
A troca de bens, serviços e conhecimentos entre os condomínios, sem a imposição de forças externas, cria uma rede de boas relações, onde o comércio e a colaboração substituem a intervenção estatal. Em vez de depender de sistemas coercitivos, cada condomínio funciona como um microcosmo autônomo que, juntos, formam um ecossistema dinâmico e próspero. Este modelo propõe que, por meio de trocas voluntárias, possamos construir uma sociedade mais saudável. Lembre-se: Ideias e somente ideias podem iluminar a escuridão.
-
 @ 35da2266:15e70970
2025-04-15 22:35:59
@ 35da2266:15e70970
2025-04-15 22:35:59NOFTr2Erm/FWn2Iwbon3TGxlXR61yy6zo3S2iG6PFV9nMUdCeqGRKNHSOUasBABwJsvmMY4WP0AePoHYuvNL6QabNxz7/tHLp3DJkj+WjDVF4US9qc48DJiiapz7sUaFucj2koDs+NkUcAZD5Ohw2RP+NS8YFQFhqQQtG3TDYqA6Lr900YqEMSR17KbhzZlNR4OqBO8yDA17Y4ltEOjxaOv/5ys5Id7qqenK1bKjPd693nU+4p60iTh/StDPKzmKZr8LFURCPH623RnjXIvwqHN00bMyiW7t1Hup6uIwZDKpVAhwjYLYUOiXlYhPtB2rQKQny5xssH8DpzNF3LJfSwFFGh4U/SjCs388WMPpd/PgtEic2grK9BBDzAeTbFLy?iv=4bG43qfls9wjBQBuTmn99g==
-
 @ 35da2266:15e70970
2025-04-15 22:34:50
@ 35da2266:15e70970
2025-04-15 22:34:50L5WDLmxdFunBoKzVVQY4l5mleg7nXQ8lRH1UAq3fNhGFN5RekZMFKZ3L2/17izs4C7n9afGPicEHrImszw1JsQWsxrw4cXKNZZbgmSw/haTJ5Ck8HmvdTi62/E2rsLlEzGgerDa2cFdOrSrLl5FzUcTSz/UB5KxMsOfgKeulIjxK+IxUuKtTXS2NFCRLBgYkr6prcjKjK7ejVOit4smZWmvs93+c4mXQxyZR4JTsjRdD0h017LG8962yDq+rjysCiiXqrCTcdN0bd/a6PVd1hdSi3q886h6+3Jqfq4aSyZ5jJPfde/pDrTPFoHtXfcUI0nFEJ7DUUk7dcjCL6XHH9NEhLe6RCZdLx7a4xbcYTWU/pHfPS2G1Vmbg9KWBs2hO?iv=hUn2MjQWE6EmnKRqcQAGiw==
-
 @ cdee943c:5e637400
2025-04-15 08:38:29
@ cdee943c:5e637400
2025-04-15 08:38:29Flotilla-Budabit is fork of Flotilla which aims to provide a first class, git-centric community experience for developers. Based on the popular Coracle client, Flotilla is a drop in replacement for Matrix/Discord/Slack, using a variation of NIP-29. This post is a result of a brainstorming session for features that would deliver the best possible user experience.
1. Repositories Overview
Goal: Browse and discover Git repositories. - Project cards showing name, description, tags, clone URL. - Buttons: Star, Watch, Fork. - Links to discussion channels and activity.
Powered by:
kind:30617
2. Branch and Tag View
Goal: Show active branches and tags with latest commits. - Branch/tag selector - HEAD pointer visualization - Timeline of commits
Powered by:
kind:30618
3. Issues Board
Goal: Track bugs, discussions, and feature requests. - Markdown issue rendering - Labels and status indicators - Threaded comments
Powered by:
kind:1621,kind:1630–1632
4. Patch Threads
Goal: View and discuss patches as threaded conversations. - Rich patch preview - Reply threads for review - Revision tracking
Powered by:
kind:1617,kind:1630–1633,NIP-10
5. Pull Request UX
Goal: Display patch series as PR-style units. - Patch stack visualization - Merge/apply status indicators - Final result commit link
Powered by:
kind:1617,kind:1631,merge-commit,applied-as-commits
6. Diff and Merge Preview
Goal: Side-by-side comparison with inline comments. - Expandable diff viewer - Merge conflict resolution UI - Apply/Close buttons
Powered by:
kind:1622,parent-commit,commit
7. Real-time Git Chat
Goal: Communicate in real-time around a repo. - Dedicated chat channels for each repo - Markdown, code snippets, and tagging support - Pinned patches, issues, and sessions
Powered by:
NIP-29,a:30617,kind:1337
8. Notifications and Mentions
Goal: Alert users to relevant events. - Mentions, assignments, and status changes - Personal notification pane
Powered by:
ptags,mentione-tags
9. Repository-Wide Search
Goal: Search patches, issues, snippets. - Full-text search with filters - Search by kind, label, commit ID
Powered by:
kind:1617,1621,1337,t,x,l,subject
10. Repository Wikis
Goal: Collaboratively edit and view project documentation. - Wiki sidebar tab - Markdown articles with versioning - Linked inline in chat
Powered by (proposed):
kind:1341(Wiki article)
kind:30617withwiki-hometag
11. Live Coding Sessions
Goal: Host real-time collaborative coding events. -
/livecodestarts a session thread - Snippets auto-tagged to session - Export as patch or wikiPowered by (proposed):
kind:1347(Live coding session)
kind:1337,kind:1622,kind:1341
Supporting Tools
1. GitHub Browser Extension
Goal: Publish GitHub content to Nostr directly. - “Share on Nostr” buttons on PRs, issues, commits
Backed by:
kind:1623,1622,1617,1621
2. VS Code Extension
Goal: Enable developers to interact with Flotilla from their IDE. - Repo feed, patch submission, issue tracking - Inline threads and comment rendering
Backed by:
kind:1617,1621,1337,163x
3. GitHub Actions Integration
Goal: Automate Nostr publishing of repo activity. - Push = repo state - PR = patch - Issue/Comment = issue - Merge = status update
Backed by:
kind:30618,1617,1621,1631
Configured via.nostr.yml -
 @ 35da2266:15e70970
2025-04-15 22:34:36
@ 35da2266:15e70970
2025-04-15 22:34:3697d+mYEJp5IRWD74WbEfsn/KgzKbGvL7O0YY6fu0xlh9p3tPkcna2hbVduDFtL85T9ayoJFYQJ/svNaYOT7YNpCJxeU0oswCRExE7cHR0KHfIk2EsMGjmGoeRlJT61oP5dO2CxXvpLBh1Xedwf+sXiAJItT3l7Xf+jRHBEa7EjNNM3vkIIuTYHVQCx31Hp3KK+fYdl6AymhS+KmxyOxNDMGvjhW2U0jaIUTffkSS8reSAcbGMx8SAMKxuhIH4O2YbgmyjiSn7CzHMD0zrhxXs/g9KS4SioT9Ka5yddSYI2YxTlAzKTKznTdhfzvuQLV0/26SXFqI9i+jtKlYKIhi/g==?iv=I4Y2WyCQqqsbTIGbWN34Nw==
-
 @ efcb5fc5:5680aa8e
2025-04-15 07:34:28
@ efcb5fc5:5680aa8e
2025-04-15 07:34:28We're living in a digital dystopia. A world where our attention is currency, our data is mined, and our mental well-being is collateral damage in the relentless pursuit of engagement. The glossy facades of traditional social media platforms hide a dark underbelly of algorithmic manipulation, curated realities, and a pervasive sense of anxiety that seeps into every aspect of our lives. We're trapped in a digital echo chamber, drowning in a sea of manufactured outrage and meaningless noise, and it's time to build an ark and sail away.
I've witnessed the evolution, or rather, the devolution, of online interaction. From the raw, unfiltered chaos of early internet chat rooms to the sterile, algorithmically controlled environments of today's social giants, I've seen the promise of connection twisted into a tool for manipulation and control. We've become lab rats in a grand experiment, our emotional responses measured and monetized, our opinions shaped and sold to the highest bidder. But there's a flicker of hope in the darkness, a chance to reclaim our digital autonomy, and that hope is NOSTR (Notes and Other Stuff Transmitted by Relays).
The Psychological Warfare of Traditional Social Media
The Algorithmic Cage: These algorithms aren't designed to enhance your life; they're designed to keep you scrolling. They feed on your vulnerabilities, exploiting your fears and desires to maximize engagement, even if it means promoting misinformation, outrage, and division.
The Illusion of Perfection: The curated realities presented on these platforms create a toxic culture of comparison. We're bombarded with images of flawless bodies, extravagant lifestyles, and seemingly perfect lives, leading to feelings of inadequacy and self-doubt.
The Echo Chamber Effect: Algorithms reinforce our existing beliefs, isolating us from diverse perspectives and creating a breeding ground for extremism. We become trapped in echo chambers where our biases are constantly validated, leading to increased polarization and intolerance.
The Toxicity Vortex: The lack of effective moderation creates a breeding ground for hate speech, cyberbullying, and online harassment. We're constantly exposed to toxic content that erodes our mental well-being and fosters a sense of fear and distrust.
This isn't just a matter of inconvenience; it's a matter of mental survival. We're being subjected to a form of psychological warfare, and it's time to fight back.
NOSTR: A Sanctuary in the Digital Wasteland
NOSTR offers a radical alternative to this toxic environment. It's not just another platform; it's a decentralized protocol that empowers users to reclaim their digital sovereignty.
User-Controlled Feeds: You decide what you see, not an algorithm. You curate your own experience, focusing on the content and people that matter to you.
Ownership of Your Digital Identity: Your data and content are yours, secured by cryptography. No more worrying about being deplatformed or having your information sold to the highest bidder.
Interoperability: Your identity works across a diverse ecosystem of apps, giving you the freedom to choose the interface that suits your needs.
Value-Driven Interactions: The "zaps" feature enables direct micropayments, rewarding creators for valuable content and fostering a culture of genuine appreciation.
Decentralized Power: No single entity controls NOSTR, making it censorship-resistant and immune to the whims of corporate overlords.
Building a Healthier Digital Future
NOSTR isn't just about escaping the toxicity of traditional social media; it's about building a healthier, more meaningful online experience.
Cultivating Authentic Connections: Focus on building genuine relationships with people who share your values and interests, rather than chasing likes and followers.
Supporting Independent Creators: Use "zaps" to directly support the artists, writers, and thinkers who inspire you.
Embracing Intellectual Diversity: Explore different NOSTR apps and communities to broaden your horizons and challenge your assumptions.
Prioritizing Your Mental Health: Take control of your digital environment and create a space that supports your well-being.
Removing the noise: Value based interactions promote value based content, instead of the constant stream of noise that traditional social media promotes.
The Time for Action is Now
NOSTR is a nascent technology, but it represents a fundamental shift in how we interact online. It's a chance to build a more open, decentralized, and user-centric internet, one that prioritizes our mental health and our humanity.
We can no longer afford to be passive consumers in the digital age. We must become active participants in shaping our online experiences. It's time to break free from the chains of algorithmic control and reclaim our digital autonomy.
Join the NOSTR movement
Embrace the power of decentralization. Let's build a digital future that's worthy of our humanity. Let us build a place where the middlemen, and the algorithms that they control, have no power over us.
In addition to the points above, here are some examples/links of how NOSTR can be used:
Simple Signup: Creating a NOSTR account is incredibly easy. You can use platforms like Yakihonne or Primal to generate your keys and start exploring the ecosystem.
X-like Client: Apps like Damus offer a familiar X-like experience, making it easy for users to transition from traditional platforms.
Sharing Photos and Videos: Clients like Olas are optimized for visual content, allowing you to share your photos and videos with your followers.
Creating and Consuming Blogs: NOSTR can be used to publish and share blog posts, fostering a community of independent creators.
Live Streaming and Audio Spaces: Explore platforms like Hivetalk and zap.stream for live streaming and audio-based interactions.
NOSTR is a powerful tool for reclaiming your digital life and building a more meaningful online experience. It's time to take control, break free from the shackles of traditional social media, and embrace the future of decentralized communication.
Get the full overview of these and other on: https://nostrapps.com/
-
 @ db11b320:05c5f7af
2025-03-29 19:04:19
@ db11b320:05c5f7af
2025-03-29 19:04:19magnet:?xt=urn:btih:9BAC9A3F98803AEA1EB28A0B60A562D7E3779710
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ c4b5369a:b812dbd6
2025-04-15 07:26:16
@ c4b5369a:b812dbd6
2025-04-15 07:26:16Offline transactions with Cashu
Over the past few weeks, I've been busy implementing offline capabilities into nutstash. I think this is one of the key value propositions of ecash, beinga a bearer instrument that can be used without internet access.
 It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!
It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!What is ecash/Cashu?
Ecash is the first cryptocurrency ever invented. It was created by David Chaum in 1983. It uses a blind signature scheme, which allows users to prove ownership of a token without revealing a link to its origin. These tokens are what we call ecash. They are bearer instruments, meaning that anyone who possesses a copy of them, is considered the owner.
Cashu is an implementation of ecash, built to tightly interact with Bitcoin, more specifically the Bitcoin lightning network. In the Cashu ecosystem,
Mintsare the gateway to the lightning network. They provide the infrastructure to access the lightning network, pay invoices and receive payments. Instead of relying on a traditional ledger scheme like other custodians do, the mint issues ecash tokens, to represent the value held by the users.How do normal Cashu transactions work?
A Cashu transaction happens when the sender gives a copy of his ecash token to the receiver. This can happen by any means imaginable. You could send the token through email, messenger, or even by pidgeon. One of the common ways to transfer ecash is via QR code.
The transaction is however not finalized just yet! In order to make sure the sender cannot double-spend their copy of the token, the receiver must do what we call a
swap. A swap is essentially exchanging an ecash token for a new one at the mint, invalidating the old token in the process. This ensures that the sender can no longer use the same token to spend elsewhere, and the value has been transferred to the receiver.
What about offline transactions?
Sending offline
Sending offline is very simple. The ecash tokens are stored on your device. Thus, no internet connection is required to access them. You can litteraly just take them, and give them to someone. The most convenient way is usually through a local transmission protocol, like NFC, QR code, Bluetooth, etc.
The one thing to consider when sending offline is that ecash tokens come in form of "coins" or "notes". The technical term we use in Cashu is
Proof. It "proofs" to the mint that you own a certain amount of value. Since these proofs have a fixed value attached to them, much like UTXOs in Bitcoin do, you would need proofs with a value that matches what you want to send. You can mix and match multiple proofs together to create a token that matches the amount you want to send. But, if you don't have proofs that match the amount, you would need to go online and swap for the needed proofs at the mint.Another limitation is, that you cannot create custom proofs offline. For example, if you would want to lock the ecash to a certain pubkey, or add a timelock to the proof, you would need to go online and create a new custom proof at the mint.
Receiving offline
You might think: well, if I trust the sender, I don't need to be swapping the token right away!
You're absolutely correct. If you trust the sender, you can simply accept their ecash token without needing to swap it immediately.
This is already really useful, since it gives you a way to receive a payment from a friend or close aquaintance without having to worry about connectivity. It's almost just like physical cash!
It does however not work if the sender is untrusted. We have to use a different scheme to be able to receive payments from someone we don't trust.
Receiving offline from an untrusted sender
To be able to receive payments from an untrusted sender, we need the sender to create a custom proof for us. As we've seen before, this requires the sender to go online.
The sender needs to create a token that has the following properties, so that the receciver can verify it offline:
- It must be locked to ONLY the receiver's public key
- It must include an
offline signature proof(DLEQ proof) - If it contains a timelock & refund clause, it must be set to a time in the future that is acceptable for the receiver
- It cannot contain duplicate proofs (double-spend)
- It cannot contain proofs that the receiver has already received before (double-spend)

If all of these conditions are met, then the receiver can verify the proof offline and accept the payment. This allows us to receive payments from anyone, even if we don't trust them.
At first glance, this scheme seems kinda useless. It requires the sender to go online, which defeats the purpose of having an offline payment system.
I beleive there are a couple of ways this scheme might be useful nonetheless:
-
Offline vending machines: Imagine you have an offline vending machine that accepts payments from anyone. The vending machine could use this scheme to verify payments without needing to go online itself. We can assume that the sender is able to go online and create a valid token, but the receiver doesn't need to be online to verify it.
-
Offline marketplaces: Imagine you have an offline marketplace where buyers and sellers can trade goods and services. Before going to the marketplace the sender already knows where he will be spending the money. The sender could create a valid token before going to the marketplace, using the merchants public key as a lock, and adding a refund clause to redeem any unspent ecash after it expires. In this case, neither the sender nor the receiver needs to go online to complete the transaction.
How to use this
Pretty much all cashu wallets allow you to send tokens offline. This is because all that the wallet needs to do is to look if it can create the desired amount from the proofs stored locally. If yes, it will automatically create the token offline.
Receiving offline tokens is currently only supported by nutstash (experimental).
To create an offline receivable token, the sender needs to lock it to the receiver's public key. Currently there is no refund clause! So be careful that you don't get accidentally locked out of your funds!

The receiver can then inspect the token and decide if it is safe to accept without a swap. If all checks are green, they can accept the token offline without trusting the sender.

The receiver will see the unswapped tokens on the wallet homescreen. They will need to manually swap them later when they are online again.
 Later when the receiver is online again, they can swap the token for a fresh one.
Later when the receiver is online again, they can swap the token for a fresh one.
Summary
We learned that offline transactions are possible with ecash, but there are some limitations. It either requires trusting the sender, or relying on either the sender or receiver to be online to verify the tokens, or create tokens that can be verified offline by the receiver.
I hope this short article was helpful in understanding how ecash works and its potential for offline transactions.
Cheers,
Gandlaf
-
 @ 5f078e90:b2bacaa3
2025-04-15 21:49:08
@ 5f078e90:b2bacaa3
2025-04-15 21:49:08Testing bidirectional-longform30023.js
This is a long form note written on Nostr using the Yakihonne.com client. The hope is that the "Hostr" bidirectional bridge will pick it up and then post in on the Hive blockchain under the @hostr account.
Ideally, hostr will be able to:
post nostr to hive only, if desired post hive to nostr only, if desired post bidirectionally This tool is very much underconstruction and being tested.
-
 @ 04c915da:3dfbecc9
2025-03-25 17:43:44
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 21335073:a244b1ad
2025-03-18 20:47:50
@ 21335073:a244b1ad
2025-03-18 20:47:50Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 5f078e90:b2bacaa3
2025-04-15 21:29:37
@ 5f078e90:b2bacaa3
2025-04-15 21:29:37This is a long form note written on Nostr using the Yakihonne.com client. The hope is that the "Hostr" bidirectional bridge will pick it up and then post in on the Hive blockchain under the @hostr account.
Ideally, hostr will be able to:
. post nostr to hive only, if desired . post hive to nostr only, if desired . post bidirectionally
This tool is very much underconstruction and being tested.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion





























