-
 @ 374ee93a:36623347
2025-05-13 11:47:55
@ 374ee93a:36623347
2025-05-13 11:47:55Chef's notes
Lovely tart rhubarb jam with the extra firey kick of fresh root ginger.
Technically a vegetable rhubarb has low pectin content so be sure to include a high pectin fruit such as lemon/cooking apple/redcurrant/gooseberry. It also quite watery so we use a slightly higher fruit to sugar ratio (1.2:1) and evaporate off some water at the beginning.
Testing for setting point: put a saucer in the freezer to chill whilst cooking the fruit, after 5 mins of a high boil with the sugar put a small blob of jam on the cold saucer and return to the freezer for 2 minutes. If the jam forms a solid wrinkle when pushed with a spoon it is ready, if it is runny continue cooking and retest every 5 mins
The recipe can be halved for a small batch but if you have lots of rhubarb to process it is better to cook double batches in separate pans because it will take much longer to heat through, this affects the colour and flavour - the jam will taste warm and mellow rather than zingy
Sterilise glass jars in a 120c oven and pot the jam hot leaving 1/4 inch head space, it will keep for 5 years unopened if the lids are well sealed and does not require water bath canning
Details
- ⏲️ Prep time: 20 mins
- 🍳 Cook time: 30 mins
- 🍽️ Servings: 6 (jars)
Ingredients
- 1.2kg Rhubarb
- 200g Grated Root Ginger
- 100g Chopped Crystalised Ginger
- 1kg Sugar
- 1 Lemon
Directions
- Chop the rhubarb into 1/2 inch pieces, peel and finely grate the fresh root ginger, chop crystalised ginger into tiny bits. Juice and quarter a lemon (discard pips) and add all these to a pan with a small amount of water
- Simmer gently for 20 mins until the lemon and rhubarb are soft then add the sugar, stir until fully dissolved
- Boil on high to reach setting point, usually at 105 degrees c or when a small blob of jam wrinkles on a cold plate instead of being runny
- Remove the lemon pieces and pot into sterilised jars
-
 @ 95543309:196c540e
2025-05-11 12:42:09
@ 95543309:196c540e
2025-05-11 12:42:09Lets see if this works with the blossom upload and without markdown hassle.
:cat:

https://blossom.primal.net/73a099f931366732c18dd60da82db6ef65bb368eb96756f07d9fa7a8a3644009.mp4
-
 @ 7459d333:f207289b
2025-05-10 10:38:56
@ 7459d333:f207289b
2025-05-10 10:38:56Description: Just as Bitcoin enabled sovereignty over money, a decentralized shipping protocol would enable sovereignty over trade. An LN/Bisq inspired shipping protocol could create an unstoppable free market.
Bitcoin gave us monetary sovereignty, freeing us from central bank manipulation, inflation, and censorship. But there's a missing link in our freedom journey: the physical world of goods.
The Problem: Even with Bitcoin, global trade remains at the mercy of: - Arbitrary tariffs and import restrictions - Political censorship of goods - Privacy invasion of shipping information - Centralized shipping carriers
The Vision: A decentralized shipping protocol with these properties:
- "Onion-routed" packages: Each carrier only knows the previous and next hop
- Bitcoin-secured multi-sig escrow: Funds locked until package delivery confirmed
- Incentive alignment: Carriers set their own fees based on risk assessment
- Privacy tiers: Options for inspected vs. sealed packages with appropriate pricing
- End-to-end sovereignty: Sender and receiver maintain control, intermediate carriers just fulfill their role
How it could work:
- Sender creates shipping request with package details and destination
- Protocol finds optimal route through independent carriers
- Each hop secured by multi-sig deposits larger than package value
- Carriers only see next hop, not ultimate destination
- Reputation systems and economic incentives maintain integrity
This creates a free market where any individual can participate as a carrier, earning Bitcoin for facilitating trade. Just like Lightning Network nodes, anyone can open "channels" with trusted partners.
Impact: This would enable true free market principles globally, making artificial trade barriers obsolete and empowering individuals to engage in voluntary exchange regardless of geographic or political boundaries.
There are a lot of challenges. But the first question is if this is a real problem and if its worth solving it.
What components would need development first? How would you solve the physical handoff challenges?
originally posted at https://stacker.news/items/976326
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 6e64b83c:94102ee8
2025-05-05 16:50:13
@ 6e64b83c:94102ee8
2025-05-05 16:50:13Nostr-static is a powerful static site generator that transforms long-form Nostr content into beautiful, standalone websites. It makes your content accessible to everyone, even those not using Nostr clients. For more information check out my previous blog post How to Create a Blog Out of Nostr Long-Form Articles
What's New in Version 0.7?
RSS and Atom Feeds
Version 0.7 brings comprehensive feed support with both RSS and Atom formats. The system automatically generates feeds for your main content, individual profiles, and tag-specific pages. These feeds are seamlessly integrated into your site's header, making them easily discoverable by feed readers and content aggregators.
This feature bridges the gap between Nostr and traditional web publishing, allowing your content to reach readers who prefer feed readers or automated content distribution systems.
Smart Content Discovery
The new tag discovery system enhances your readers' experience by automatically finding and recommending relevant articles from the Nostr network. It works by:
- Analyzing the tags in your articles
- Fetching popular articles from Nostr that share these tags
- Using configurable weights to rank these articles based on:
- Engagement metrics (reactions, reposts, replies)
- Zap statistics (amount, unique zappers, average zap size)
- Content quality signals (report penalties)
This creates a dynamic "Recommended Articles" section that helps readers discover more content they might be interested in, all while staying within the Nostr ecosystem.
See the new features yourself by visiting our demo at: https://blog.nostrize.me
-
 @ 6e0ea5d6:0327f353
2025-05-04 14:53:42
@ 6e0ea5d6:0327f353
2025-05-04 14:53:42Amico mio, ascolta bene!
Without hesitation, the woman you attract with lies is not truly yours. Davvero, she is the temporary property of the illusion you’ve built to seduce her. And every illusion, sooner or later, crumbles.
Weak men sell inflated versions of themselves. They talk about what they don’t have, promise what they can’t sustain, adorn their empty selves with words that are nothing more than a coat of paint. And they do this thinking that, later, they’ll be able to "show who they really are." Fatal mistake, cazzo!
The truth, amico mio, is not something that appears at the end. It is what holds up the whole beginning.
The woman who approaches a lie may smile at first — but she is smiling at the theater, not at the actor. When the curtains fall, what she will see is not a man. It will be a character tired of performing, begging for love from a self-serving audience in the front row.
That’s why I always point out that lying to win a woman’s heart is the same as sabotaging your own nature. The woman who comes through an invented version of you will be the first to leave when the veil of lies tears apart. Not out of cruelty, but out of consistency with her own interest. Fine... She didn’t leave you, but rather, that version of yourself never truly existed to be left behind.
A worthy man presents himself without deceptive adornments. And those who stay, stay because they know exactly who they are choosing as a man. That’s what differentiates forged seduction from the convenience of love built on honor, loyalty, and respect.
Ah, amico mio, I remember well. It was lunch on an autumn day in Catania. Mediterranean heat, and the Nero D'Avola wine from midday clinging to the lips like dried blood. Sitting in the shade of a lemon tree planted right by my grandfather's vineyard entrance, my uncle — the oldest of my father’s brothers — spoke little, but when he called us to sit by his side, all the nephews would quiet down to listen. And in my youth, he told me something that has never left my mind.
“In Sicily, the woman who endures the silence of a man about his business is more loyal than the one who is enchanted by speeches about what he does or how much he earns. Perchè, figlio mio, the first one has seen the truth. The second one, only a false shine.”
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
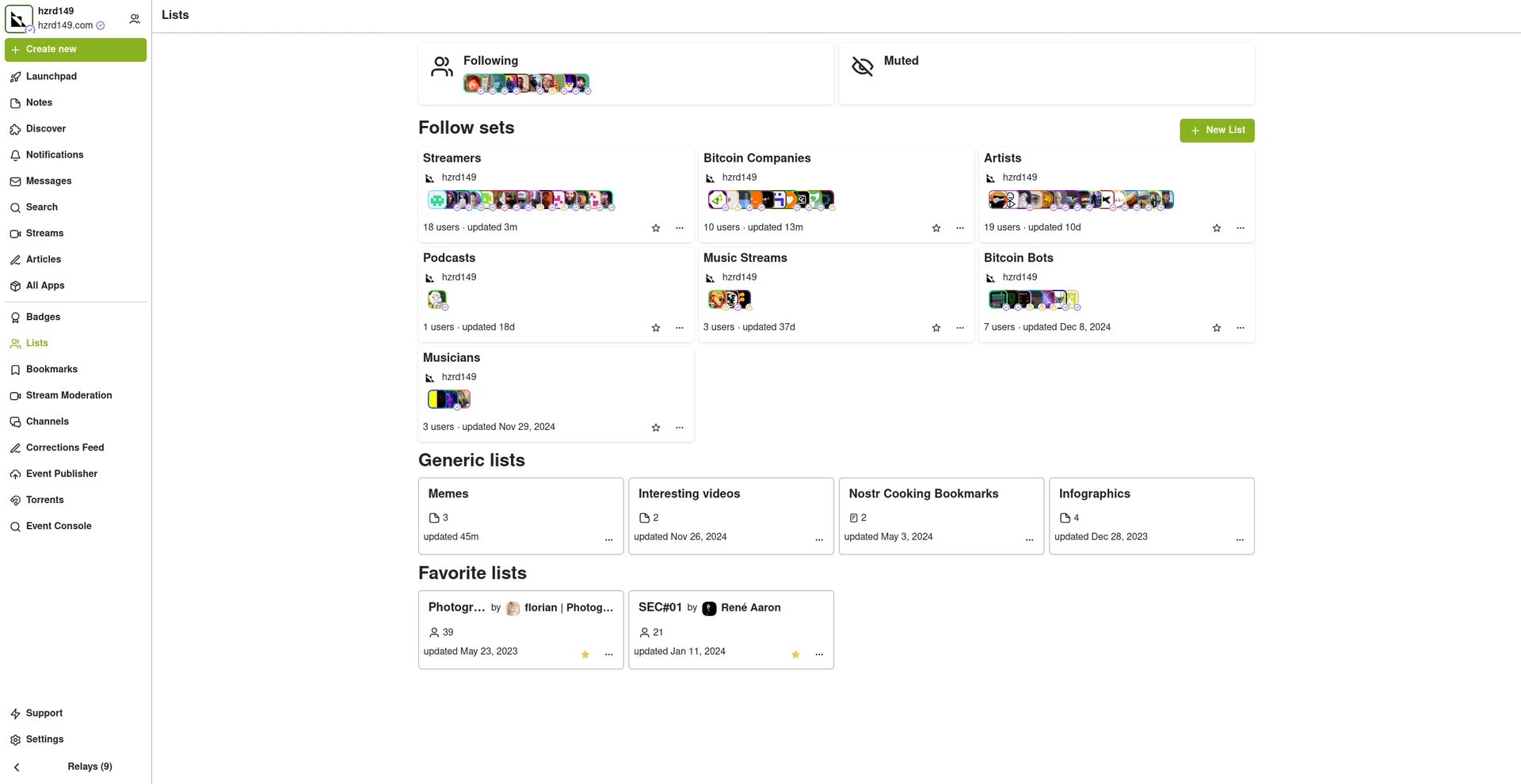
 @ 266815e0:6cd408a5
2025-05-02 22:24:59
@ 266815e0:6cd408a5
2025-05-02 22:24:59Its been six long months of refactoring code and building out to the applesauce packages but the app is stable enough for another release.
This update is pretty much a full rewrite of the non-visible parts of the app. all the background services were either moved out to the applesauce packages or rewritten, the result is that noStrudel is a little faster and much more consistent with connections and publishing.
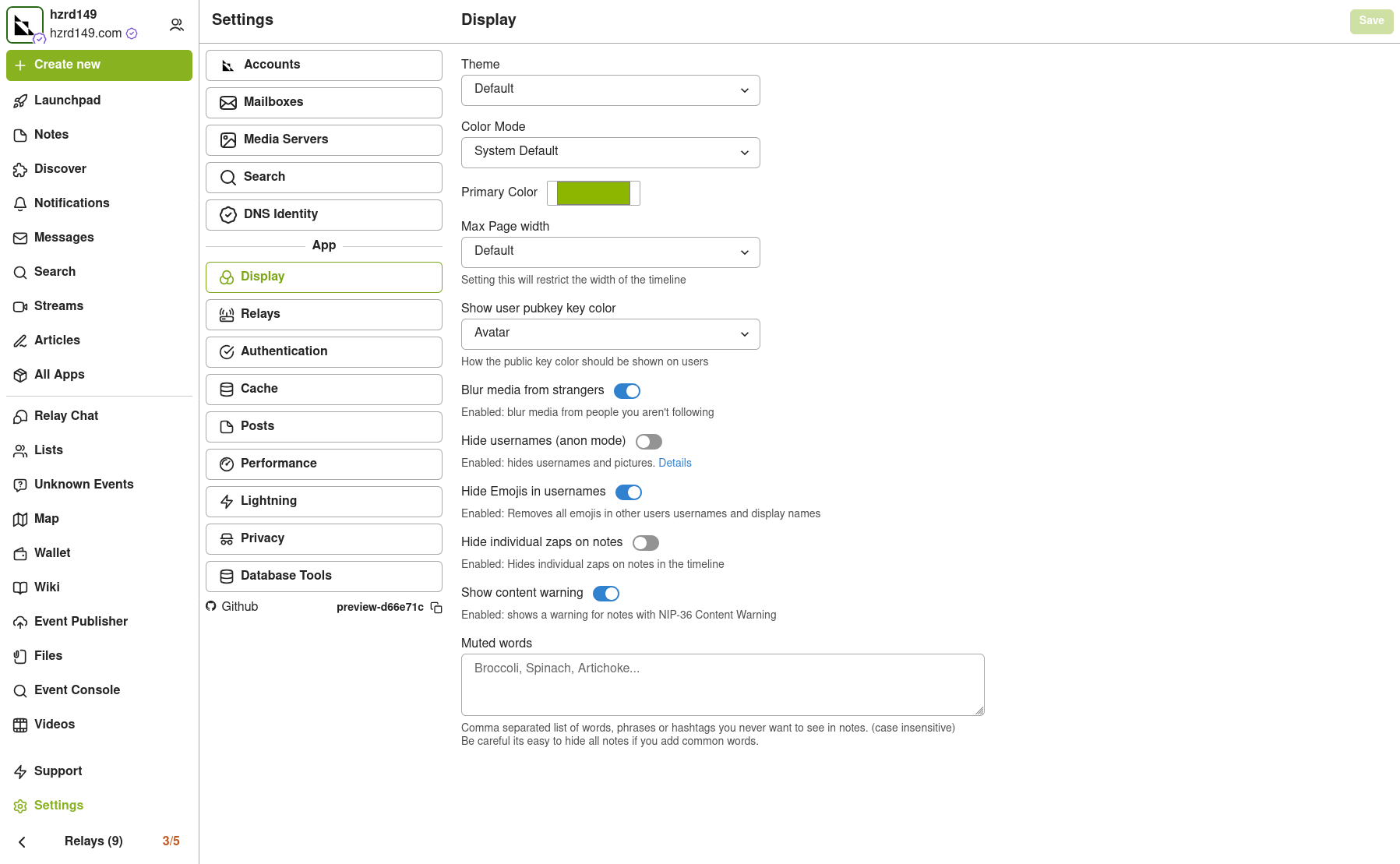
New layout
The app has a new layout now, it takes advantage of the full desktop screen and looks a little better than it did before.
Removed NIP-72 communities
The NIP-72 communities are no longer part of the app, if you want to continue using them there are still a few apps that support them ( like satellite.earth ) but noStrudel won't support them going forward.
The communities where interesting but ultimately proved too have some fundamental flaws, most notably that all posts had to be approved by a moderator. There were some good ideas on how to improve it but they would have only been patches and wouldn't have fixed the underlying issues.
I wont promise to build it into noStrudel, but NIP-29 (relay based groups) look a lot more promising and already have better moderation abilities then NIP-72 communities could ever have.
Settings view
There is now a dedicated settings view, so no more hunting around for where the relays are set or trying to find how to add another account. its all in one place now
Cleaned up lists
The list views are a little cleaner now, and they have a simple edit modal
New emoji picker
Just another small improvement that makes the app feel more complete.
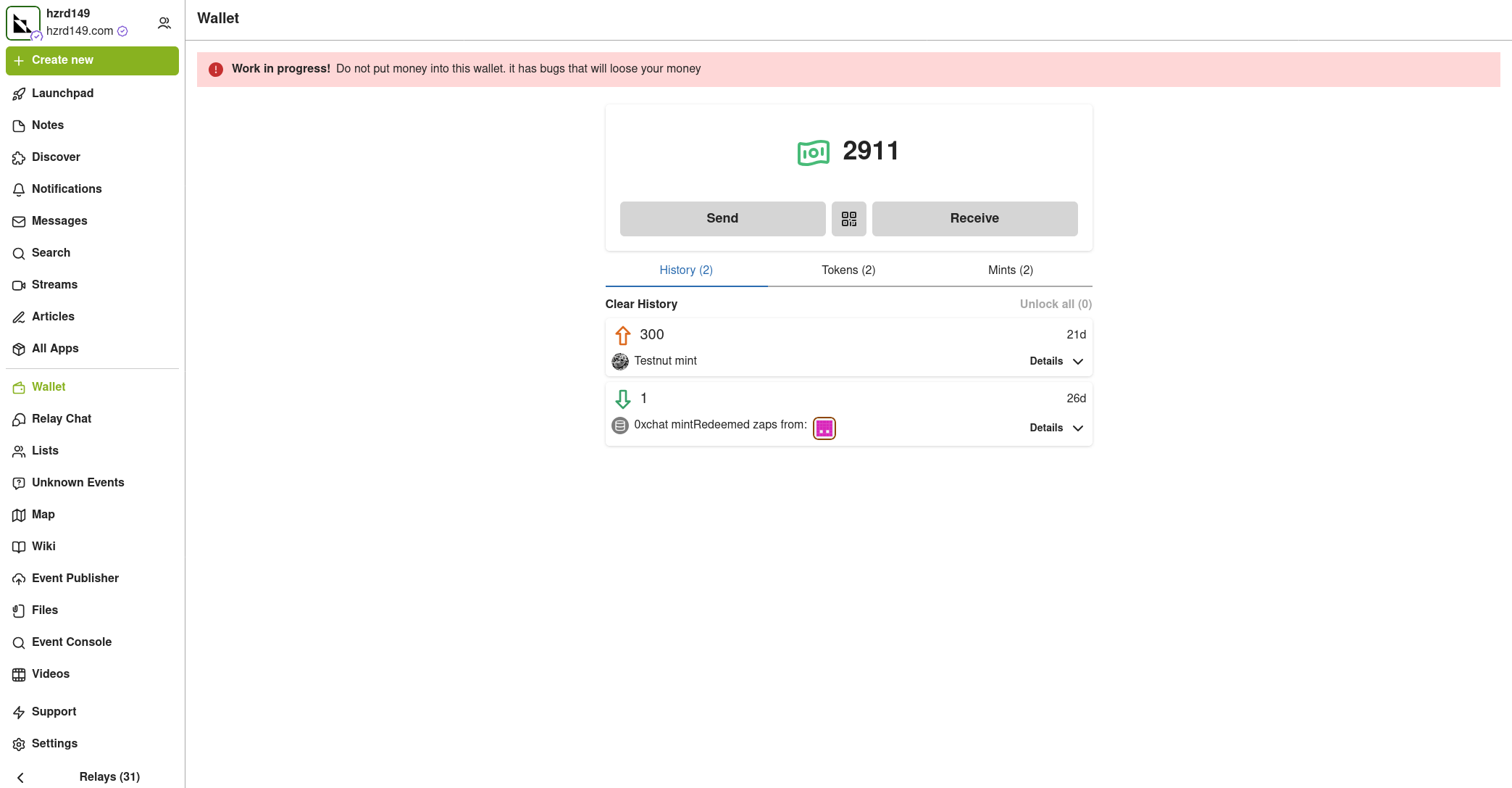
Experimental Wallet
There is a new "wallet" view in the app that lets you manage your NIP-60 cashu wallet. its very experimental and probably won't work for you, but its there and I hope to finish it up so the app can support NIP-61 nutzaps.
WARNING: Don't feed the wallet your hard earned sats, it will eat them!
Smaller improvements
- Added NSFW flag for replies
- Updated NIP-48 bunker login to work with new spec
- Linkfy BIPs
- Added 404 page
- Add NIP-22 comments under badges, files, and articles
- Add max height to timeline notes
- Fix articles view freezing on load
- Add option to mirror blobs when sharing notes
- Remove "open in drawer" for notes
-
 @ 088436cd:9d2646cc
2025-05-01 21:01:55
@ 088436cd:9d2646cc
2025-05-01 21:01:55The arrival of the coronavirus brought not only illness and death but also fear and panic. In such an environment of uncertainty, people have naturally stocked up on necessities, not knowing when things will return to normal.
Retail shelves have been cleared out, and even online suppliers like Amazon and Walmart are out of stock for some items. Independent sellers on these e-commerce platforms have had to fill the gap. With the huge increase in demand, they have found that their inventory has skyrocketed in value.
Many in need of these items (e.g. toilet paper, hand sanitizer and masks) balk at the new prices. They feel they are being taken advantage of in a time of need and call for intervention by the government to lower prices. The government has heeded that call, labeling the independent sellers as "price gougers" and threatening sanctions if they don't lower their prices. Amazon has suspended seller accounts and law enforcement at all levels have threatened to prosecute. Prices have dropped as a result and at first glance this seems like a victory for fair play. But, we will have to dig deeper to understand the unseen consequences of this intervention.
We must look at the economics of the situation, how supply and demand result in a price and how that price acts as a signal that goes out to everyone, informing them of underlying conditions in the economy and helping coordinate their actions.
It all started with a rise in demand. Given a fixed supply (e.g., the limited stock on shelves and in warehouses), an increase in demand inevitably leads to higher prices. Most people are familiar with this phenomenon, such as paying more for airline tickets during holidays or surge pricing for rides.
Higher prices discourage less critical uses of scarce resources. For example, you might not pay $1,000 for a plane ticket to visit your aunt if you can get one for $100 the following week, but someone else might pay that price to visit a dying relative. They value that plane seat more than you.
*** During the crisis, demand surged and their shelves emptied even though
However, retail outlets have not raised prices. They have kept them low, so the low-value uses of things like toilet paper, masks and hand sanitizer has continued. Often, this "use" just takes the form of hoarding. At everyday low prices, it makes sense to buy hundreds of rolls and bottles. You know you will use them eventually, so why not stock up? And, with all those extra supplies in the closet and basement, you don't need to change your behavior much. You don't have to ration your use.
At the low prices, these scarce resources got bought up faster and faster until there was simply none left. The reality of the situation became painfully clear to those who didn't panic and got to the store late: You have no toilet paper and you're not going to any time soon.
However, if prices had been allowed to rise, a number of effects would have taken place that would have coordinated the behavior of everyone so that valuable resources would not have been wasted or hoarded, and everyone could have had access to what they needed.
On the demand side, if prices had been allowed to rise, people would have begun to self-ration. You might leave those extra plies on the roll next time if you know they will cost ten times as much to replace. Or, you might choose to clean up a spill with a rag rather than disposable tissue. Most importantly, you won't hoard as much. That 50th bottle of hand sanitizer might just not be worth it at the new, high price. You'll leave it on the shelf for someone else who may have none.
On the supply side, higher prices would have incentivized people to offer up more of their stockpiles for sale. If you have a pallet full of toilet paper in your basement and all of the sudden they are worth $15 per roll, you might just list a few online. But, if it is illegal to do so, you probably won't.
Imagine you run a business installing insulation and have a few thousand respirator masks on hand for your employees. During a pandemic, it is much more important that people breathe filtered air than that insulation get installed, and that fact is reflected in higher prices. You will sell your extra masks at the higher price rather than store them for future insulation jobs, and the scarce resource will be put to its most important use.
Producers of hand sanitizer would go into overdrive if prices were allowed to rise. They would pay their employees overtime, hire new ones, and pay a premium for their supplies, making sure their raw materials don't go to less important uses.
These kinds of coordinated actions all across the economy would be impossible without real prices to guide them. How do you know if it makes sense to spend an extra $10k bringing a thousand masks to market unless you know you can get more than $10 per mask? If the price is kept artificially low, you simply can't do it. The money just isn't there.
These are the immediate effects of a price change, but incredibly, price changes also coordinate people's actions across space and time.
Across space, there are different supply and demand conditions in different places, and thus prices are not uniform. We know some places are real "hot spots" for the virus, while others are mostly unaffected. High demand in the hot spots leads to higher prices there, which attracts more of the resource to those areas. Boxes and boxes of essential items would pour in where they are needed most from where they are needed least, but only if prices were allowed to adjust freely.
This would be accomplished by individuals and businesses buying low in the unaffected areas, selling high in the hot spots and subtracting their labor and transportation costs from the difference. Producers of new supply would know exactly where it is most needed and ship to the high-demand, high-price areas first. The effect of these actions is to increase prices in the low demand areas and reduce them in the high demand areas. People in the low demand areas will start to self-ration more, reflecting the reality of their neighbors, and people in the hotspots will get some relief.
However, by artificially suppressing prices in the hot spot, people there will simply buy up the available supply and run out, and it will be cost prohibitive to bring in new supply from low-demand areas.
Prices coordinate economic actions across time as well. Just as entrepreneurs and businesses can profit by transporting scarce necessities from low-demand to high-demand areas, they can also profit by buying in low-demand times and storing their merchandise for when it is needed most.
Just as allowing prices to freely adjust in one area relative to another will send all the right signals for the optimal use of a scarce resource, allowing prices to freely adjust over time will do the same.
When an entrepreneur buys up resources during low-demand times in anticipation of a crisis, she restricts supply ahead of the crisis, which leads to a price increase. She effectively bids up the price. The change in price affects consumers and producers in all the ways mentioned above. Consumers self-ration more, and producers bring more of the resource to market.
Our entrepreneur has done a truly incredible thing. She has predicted the future, and by so doing has caused every individual in the economy to prepare for a shortage they don't even know is coming! And, by discouraging consumption and encouraging production ahead of time, she blunts the impact the crisis will have. There will be more of the resource to go around when it is needed most.
On top of this, our entrepreneur still has her stockpile she saved back when everyone else was blithely using it up. She can now further mitigate the damage of the crisis by selling her stock during the worst of it, when people are most desperate for relief. She will know when this is because the price will tell her, but only if it is allowed to adjust freely. When the price is at its highest is when people need the resource the most, and those willing to pay will not waste it or hoard it. They will put it to its highest valued use.
The economy is like a big bus we are all riding in, going down a road with many twists and turns. Just as it is difficult to see into the future, it is difficult to see out the bus windows at the road ahead.
On the dashboard, we don't have a speedometer or fuel gauge. Instead we have all the prices for everything in the economy. Prices are what tell us the condition of the bus and the road. They tell us everything. Without them, we are blind.
Good times are a smooth road. Consumer prices and interest rates are low, investment returns are steady. We hit the gas and go fast. But, the road is not always straight and smooth. Sometimes there are sharp turns and rough patches. Successful entrepreneurs are the ones who can see what is coming better than everyone else. They are our navigators.
When they buy up scarce resources ahead of a crisis, they are hitting the brakes and slowing us down. When they divert resources from one area to another, they are steering us onto a smoother path. By their actions in the market, they adjust the prices on our dashboard to reflect the conditions of the road ahead, so we can prepare for, navigate and get through the inevitable difficulties we will face.
Interfering with the dashboard by imposing price floors or price caps doesn't change the conditions of the road (the number of toilet paper rolls in existence hasn't changed). All it does is distort our perception of those conditions. We think the road is still smooth--our heavy foot stomping the gas--as we crash onto a rocky dirt road at 80 miles per hour (empty shelves at the store for weeks on end).
Supply, demand and prices are laws of nature. All of this is just how things work. It isn't right or wrong in a moral sense. Price caps lead to waste, shortages and hoarding as surely as water flows downhill. The opposite--allowing prices to adjust freely--leads to conservation of scarce resources and their being put to their highest valued use. And yes, it leads to profits for the entrepreneurs who were able to correctly predict future conditions, and losses for those who weren't.
Is it fair that they should collect these profits? On the one hand, anyone could have stocked up on toilet paper, hand sanitizer and face masks at any time before the crisis, so we all had a fair chance to get the supplies cheaply. On the other hand, it just feels wrong that some should profit so much at a time when there is so much need.
Our instinct in the moment is to see the entrepreneur as a villain, greedy "price gouger". But we don't see the long chain of economic consequences the led to the situation we feel is unfair.
If it weren't for anti-price-gouging laws, the major retailers would have raised their prices long before the crisis became acute. When they saw demand outstrip supply, they would have raised prices, not by 100 fold, but gradually and long before anyone knew how serious things would have become. Late comers would have had to pay more, but at least there would be something left on the shelf.
As an entrepreneur, why take risks trying to anticipate the future if you can't reap the reward when you are right? Instead of letting instead of letting entrepreneurs--our navigators--guide us, we are punishing and vilifying them, trying to force prices to reflect a reality that simply doesn't exist.
In a crisis, more than any other time, prices must be allowed to fluctuate. To do otherwise is to blind ourselves at a time when danger and uncertainty abound. It is economic suicide.
In a crisis, there is great need, and the way to meet that need is not by pretending it's not there, by forcing prices to reflect a world where there isn't need. They way to meet the need is the same it has always been, through charity.
If the people in government want to help, the best way for the to do so is to be charitable and reduce their taxes and fees as much as possible, ideally to zero in a time of crisis. Amazon, for example, could instantly reduce the price of all crisis related necessities by 20% if they waived their fee. This would allow for more uses by more people of these scarce supplies as hoarders release their stockpiles on to the market, knowing they can get 20% more for their stock. Governments could reduce or eliminate their tax burden on high-demand, crisis-related items and all the factors that go into their production, with the same effect: a reduction in prices and expansion of supply. All of us, including the successful entrepreneurs and the wealthy for whom high prices are not a great burden, could donate to relief efforts.
These ideas are not new or untested. This is core micro economics. It has been taught for hundreds of years in universities the world over. The fact that every crisis that comes along stirs up ire against entrepreneurs indicates not that the economics is wrong, but that we have a strong visceral reaction against what we perceive to be unfairness. This is as it should be. Unfairness is wrong and the anger it stirs in us should compel us to right the wrong. Our anger itself isn't wrong, it's just misplaced.
Entrepreneurs didn't cause the prices to rise. Our reaction to a virus did that. We saw a serious threat and an uncertain future and followed our natural impulse to hoard. Because prices at major retail suppliers didn't rise, that impulse ran rampant and we cleared the shelves until there was nothing left. We ran the bus right off the road and them blamed the entrepreneurs for showing us the reality of our situation, for shaking us out of the fantasy of low prices.
All of this is not to say that entrepreneurs are high-minded public servants. They are just doing their job. Staking your money on an uncertain future is a risky business. There are big risks and big rewards. Most entrepreneurs just scrape by or lose their capital in failed ventures.
However, the ones that get it right must be allowed to keep their profits, or else no one will try and we'll all be driving blind. We need our navigators. It doesn't even matter if they know all the positive effects they are having on the rest of us and the economy as a whole. So long as they are buying low and selling high--so long as they are doing their job--they will be guiding the rest of us through the good times and the bad, down the open road and through the rough spots.
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ a008def1:57a3564d
2025-04-30 17:52:11
@ a008def1:57a3564d
2025-04-30 17:52:11A Vision for #GitViaNostr
Git has long been the standard for version control in software development, but over time, we has lost its distributed nature. Originally, Git used open, permissionless email for collaboration, which worked well at scale. However, the rise of GitHub and its centralized pull request (PR) model has shifted the landscape.
Now, we have the opportunity to revive Git's permissionless and distributed nature through Nostr!
We’ve developed tools to facilitate Git collaboration via Nostr, but there are still significant friction that prevents widespread adoption. This article outlines a vision for how we can reduce those barriers and encourage more repositories to embrace this approach.
First, we’ll review our progress so far. Then, we’ll propose a guiding philosophy for our next steps. Finally, we’ll discuss a vision to tackle specific challenges, mainly relating to the role of the Git server and CI/CD.
I am the lead maintainer of ngit and gitworkshop.dev, and I’ve been fortunate to work full-time on this initiative for the past two years, thanks to an OpenSats grant.
How Far We’ve Come
The aim of #GitViaNostr is to liberate discussions around code collaboration from permissioned walled gardens. At the core of this collaboration is the process of proposing and applying changes. That's what we focused on first.
Since Nostr shares characteristics with email, and with NIP34, we’ve adopted similar primitives to those used in the patches-over-email workflow. This is because of their simplicity and that they don’t require contributors to host anything, which adds reliability and makes participation more accessible.
However, the fork-branch-PR-merge workflow is the only model many developers have known, and changing established workflows can be challenging. To address this, we developed a new workflow that balances familiarity, user experience, and alignment with the Nostr protocol: the branch-PR-merge model.
This model is implemented in ngit, which includes a Git plugin that allows users to engage without needing to learn new commands. Additionally, gitworkshop.dev offers a GitHub-like interface for interacting with PRs and issues. We encourage you to try them out using the quick start guide and share your feedback. You can also explore PRs and issues with gitplaza.
For those who prefer the patches-over-email workflow, you can still use that approach with Nostr through gitstr or the
ngit sendandngit listcommands, and explore patches with patch34.The tools are now available to support the core collaboration challenge, but we are still at the beginning of the adoption curve.
Before we dive into the challenges—such as why the Git server setup can be jarring and the possibilities surrounding CI/CD—let’s take a moment to reflect on how we should approach the challenges ahead of us.
Philosophy
Here are some foundational principles I shared a few years ago:
- Let Git be Git
- Let Nostr be Nostr
- Learn from the successes of others
I’d like to add one more:
- Embrace anarchy and resist monolithic development.
Micro Clients FTW
Nostr celebrates simplicity, and we should strive to maintain that. Monolithic developments often lead to unnecessary complexity. Projects like gitworkshop.dev, which aim to cover various aspects of the code collaboration experience, should not stifle innovation.
Just yesterday, the launch of following.space demonstrated how vibe-coded micro clients can make a significant impact. They can be valuable on their own, shape the ecosystem, and help push large and widely used clients to implement features and ideas.
The primitives in NIP34 are straightforward, and if there are any barriers preventing the vibe-coding of a #GitViaNostr app in an afternoon, we should work to eliminate them.
Micro clients should lead the way and explore new workflows, experiences, and models of thinking.
Take kanbanstr.com. It provides excellent project management and organization features that work seamlessly with NIP34 primitives.
From kanban to code snippets, from CI/CD runners to SatShoot—may a thousand flowers bloom, and a thousand more after them.
Friction and Challenges
The Git Server
In #GitViaNostr, maintainers' branches (e.g.,
master) are hosted on a Git server. Here’s why this approach is beneficial:- Follows the original Git vision and the "let Git be Git" philosophy.
- Super efficient, battle-tested, and compatible with all the ways people use Git (e.g., LFS, shallow cloning).
- Maintains compatibility with related systems without the need for plugins (e.g., for build and deployment).
- Only repository maintainers need write access.
In the original Git model, all users would need to add the Git server as a 'git remote.' However, with ngit, the Git server is hidden behind a Nostr remote, which enables:
- Hiding complexity from contributors and users, so that only maintainers need to know about the Git server component to start using #GitViaNostr.
- Maintainers can easily swap Git servers by updating their announcement event, allowing contributors/users using ngit to automatically switch to the new one.
Challenges with the Git Server
While the Git server model has its advantages, it also presents several challenges:
- Initial Setup: When creating a new repository, maintainers must select a Git server, which can be a jarring experience. Most options come with bloated social collaboration features tied to a centralized PR model, often difficult or impossible to disable.
-
Manual Configuration: New repositories require manual configuration, including adding new maintainers through a browser UI, which can be cumbersome and time-consuming.
-
User Onboarding: Many Git servers require email sign-up or KYC (Know Your Customer) processes, which can be a significant turn-off for new users exploring a decentralized and permissionless alternative to GitHub.
Once the initial setup is complete, the system works well if a reliable Git server is chosen. However, this is a significant "if," as we have become accustomed to the excellent uptime and reliability of GitHub. Even professionally run alternatives like Codeberg can experience downtime, which is frustrating when CI/CD and deployment processes are affected. This problem is exacerbated when self-hosting.
Currently, most repositories on Nostr rely on GitHub as the Git server. While maintainers can change servers without disrupting their contributors, this reliance on a centralized service is not the decentralized dream we aspire to achieve.
Vision for the Git Server
The goal is to transform the Git server from a single point of truth and failure into a component similar to a Nostr relay.
Functionality Already in ngit to Support This
-
State on Nostr: Store the state of branches and tags in a Nostr event, removing reliance on a single server. This validates that the data received has been signed by the maintainer, significantly reducing the trust requirement.
-
Proxy to Multiple Git Servers: Proxy requests to all servers listed in the announcement event, adding redundancy and eliminating the need for any one server to match GitHub's reliability.
Implementation Requirements
To achieve this vision, the Nostr Git server implementation should:
-
Implement the Git Smart HTTP Protocol without authentication (no SSH) and only accept pushes if the reference tip matches the latest state event.
-
Avoid Bloat: There should be no user authentication, no database, no web UI, and no unnecessary features.
-
Automatic Repository Management: Accept or reject new repositories automatically upon the first push based on the content of the repository announcement event referenced in the URL path and its author.
Just as there are many free, paid, and self-hosted relays, there will be a variety of free, zero-step signup options, as well as self-hosted and paid solutions.
Some servers may use a Web of Trust (WoT) to filter out spam, while others might impose bandwidth or repository size limits for free tiers or whitelist specific npubs.
Additionally, some implementations could bundle relay and blossom server functionalities to unify the provision of repository data into a single service. These would likely only accept content related to the stored repositories rather than general social nostr content.
The potential role of CI / CD via nostr DVMs could create the incentives for a market of highly reliable free at the point of use git servers.
This could make onboarding #GitViaNostr repositories as easy as entering a name and selecting from a multi-select list of Git server providers that announce via NIP89.
!(image)[https://image.nostr.build/badedc822995eb18b6d3c4bff0743b12b2e5ac018845ba498ce4aab0727caf6c.jpg]
Git Client in the Browser
Currently, many tasks are performed on a Git server web UI, such as:
- Browsing code, commits, branches, tags, etc.
- Creating and displaying permalinks to specific lines in commits.
- Merging PRs.
- Making small commits and PRs on-the-fly.
Just as nobody goes to the web UI of a relay (e.g., nos.lol) to interact with notes, nobody should need to go to a Git server to interact with repositories. We use the Nostr protocol to interact with Nostr relays, and we should use the Git protocol to interact with Git servers. This situation has evolved due to the centralization of Git servers. Instead of being restricted to the view and experience designed by the server operator, users should be able to choose the user experience that works best for them from a range of clients. To facilitate this, we need a library that lowers the barrier to entry for creating these experiences. This library should not require a full clone of every repository and should not depend on proprietary APIs. As a starting point, I propose wrapping the WASM-compiled gitlib2 library for the web and creating useful functions, such as showing a file, which utilizes clever flags to minimize bandwidth usage (e.g., shallow clone, noblob, etc.).
This approach would not only enhance clients like gitworkshop.dev but also bring forth a vision where Git servers simply run the Git protocol, making vibe coding Git experiences even better.
song
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 created song with a complementary vision that has shaped how I see the role of the git server. Its a self-hosted, nostr-permissioned git server with a relay baked in. Its currently a WIP and there are some compatability with ngit that we need to work out.
We collaborated on the nostr-permissioning approach now reflected in nip34.
I'm really excited to see how this space evolves.
CI/CD
Most projects require CI/CD, and while this is often bundled with Git hosting solutions, it is currently not smoothly integrated into #GitViaNostr yet. There are many loosely coupled options, such as Jenkins, Travis, CircleCI, etc., that could be integrated with Nostr.
However, the more exciting prospect is to use DVMs (Data Vending Machines).
DVMs for CI/CD
Nostr Data Vending Machines (DVMs) can provide a marketplace of CI/CD task runners with Cashu for micro payments.
There are various trust levels in CI/CD tasks:
- Tasks with no secrets eg. tests.
- Tasks using updatable secrets eg. API keys.
- Unverifiable builds and steps that sign with Android, Nostr, or PGP keys.
DVMs allow tasks to be kicked off with specific providers using a Cashu token as payment.
It might be suitable for some high-compute and easily verifiable tasks to be run by the cheapest available providers. Medium trust tasks could be run by providers with a good reputation, while high trust tasks could be run on self-hosted runners.
Job requests, status, and results all get published to Nostr for display in Git-focused Nostr clients.
Jobs could be triggered manually, or self-hosted runners could be configured to watch a Nostr repository and kick off jobs using their own runners without payment.
But I'm most excited about the prospect of Watcher Agents.
CI/CD Watcher Agents
AI agents empowered with a NIP60 Cashu wallet can run tasks based on activity, such as a push to master or a new PR, using the most suitable available DVM runner that meets the user's criteria. To keep them running, anyone could top up their NIP60 Cashu wallet; otherwise, the watcher turns off when the funds run out. It could be users, maintainers, or anyone interested in helping the project who could top up the Watcher Agent's balance.
As aluded to earlier, part of building a reputation as a CI/CD provider could involve running reliable hosting (Git server, relay, and blossom server) for all FOSS Nostr Git repositories.
This provides a sustainable revenue model for hosting providers and creates incentives for many free-at-the-point-of-use hosting providers. This, in turn, would allow one-click Nostr repository creation workflows, instantly hosted by many different providers.
Progress to Date
nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr and nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 have been working on a runner that uses GitHub Actions YAML syntax (using act) for the dvm-cicd-runner and takes Cashu payment. You can see example runs on GitWorkshop. It currently takes testnuts, doesn't give any change, and the schema will likely change.
Note: The actions tab on GitWorkshop is currently available on all repositories if you turn on experimental mode (under settings in the user menu).
It's a work in progress, and we expect the format and schema to evolve.
Easy Web App Deployment
For those disapointed not to find a 'Nostr' button to import a git repository to Vercel menu: take heart, they made it easy. vercel.com_import_options.png there is a vercel cli that can be easily called in CI / CD jobs to kick of deployments. Not all managed solutions for web app deployment (eg. netlify) make it that easy.
Many More Opportunities
Large Patches via Blossom
I would be remiss not to mention the large patch problem. Some patches are too big to fit into Nostr events. Blossom is perfect for this, as it allows these larger patches to be included in a blossom file and referenced in a new patch kind.
Enhancing the #GitViaNostr Experience
Beyond the large patch issue, there are numerous opportunities to enhance the #GitViaNostr ecosystem. We can focus on improving browsing, discovery, social and notifications. Receiving notifications on daily driver Nostr apps is one of the killer features of Nostr. However, we must ensure that Git-related notifications are easily reviewable, so we don’t miss any critical updates.
We need to develop tools that cater to our curiosity—tools that enable us to discover and follow projects, engage in discussions that pique our interest, and stay informed about developments relevant to our work.
Additionally, we should not overlook the importance of robust search capabilities and tools that facilitate migrations.
Concluding Thoughts
The design space is vast. Its an exciting time to be working on freedom tech. I encourage everyone to contribute their ideas and creativity and get vibe-coding!
I welcome your honest feedback on this vision and any suggestions you might have. Your insights are invaluable as we collaborate to shape the future of #GitViaNostr. Onward.
Contributions
To conclude, I want to acknowledge some the individuals who have made recent code contributions related to #GitViaNostr:
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 (gitstr, song, patch34), nostr:npub1useke4f9maul5nf67dj0m9sq6jcsmnjzzk4ycvldwl4qss35fvgqjdk5ks (gitplaza)
nostr:npub1elta7cneng3w8p9y4dw633qzdjr4kyvaparuyuttyrx6e8xp7xnq32cume (ngit contributions, git-remote-blossom),nostr:npub16p8v7varqwjes5hak6q7mz6pygqm4pwc6gve4mrned3xs8tz42gq7kfhdw (SatShoot, Flotilla-Budabit), nostr:npub1ehhfg09mr8z34wz85ek46a6rww4f7c7jsujxhdvmpqnl5hnrwsqq2szjqv (Flotilla-Budabit, Nostr Git Extension), nostr:npub1ahaz04ya9tehace3uy39hdhdryfvdkve9qdndkqp3tvehs6h8s5slq45hy (gnostr and experiments), and others.
nostr:npub1uplxcy63up7gx7cladkrvfqh834n7ylyp46l3e8t660l7peec8rsd2sfek (git-remote-nostr)
Project Management nostr:npub1ltx67888tz7lqnxlrg06x234vjnq349tcfyp52r0lstclp548mcqnuz40t (kanbanstr) Code Snippets nostr:npub1ygzj9skr9val9yqxkf67yf9jshtyhvvl0x76jp5er09nsc0p3j6qr260k2 (nodebin.io) nostr:npub1r0rs5q2gk0e3dk3nlc7gnu378ec6cnlenqp8a3cjhyzu6f8k5sgs4sq9ac (snipsnip.dev)
CI / CD nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr
and for their nostr:npub1c03rad0r6q833vh57kyd3ndu2jry30nkr0wepqfpsm05vq7he25slryrnw nostr:npub1qqqqqq2stely3ynsgm5mh2nj3v0nk5gjyl3zqrzh34hxhvx806usxmln03 and nostr:npub1l5sga6xg72phsz5422ykujprejwud075ggrr3z2hwyrfgr7eylqstegx9z for their testing, feedback, ideas and encouragement.
Thank you for your support and collaboration! Let me know if I've missed you.
-
 @ 6be5cc06:5259daf0
2025-04-28 01:05:49
@ 6be5cc06:5259daf0
2025-04-28 01:05:49Eu reconheço que Deus, e somente Deus, é o soberano legítimo sobre todas as coisas. Nenhum homem, nenhuma instituição, nenhum parlamento tem autoridade para usurpar aquilo que pertence ao Rei dos reis. O Estado moderno, com sua pretensão totalizante, é uma farsa blasfema diante do trono de Cristo. Não aceito outro senhor.
A Lei que me guia não é a ditada por burocratas, mas a gravada por Deus na própria natureza humana. A razão, quando iluminada pela fé, é suficiente para discernir o que é justo. Rejeito as leis arbitrárias que pretendem legitimar o roubo, o assassinato ou a escravidão em nome da ordem. A justiça não nasce do decreto, mas da verdade.
Acredito firmemente na propriedade privada como extensão da própria pessoa. Aquilo que é fruto do meu trabalho, da minha criatividade, da minha dedicação, dos dons a mim concedidos por Deus, pertence a mim por direito natural. Ninguém pode legitimamente tomar o que é meu sem meu consentimento. Todo imposto é uma agressão; toda expropriação, um roubo. Defendo a liberdade econômica não por idolatria ao mercado, mas porque a liberdade é condição necessária para a virtude.
Assumo o Princípio da Não Agressão como o mínimo ético que devo respeitar. Não iniciarei o uso da força contra ninguém, nem contra sua propriedade. Exijo o mesmo de todos. Mas sei que isso não basta. O PNA delimita o que não devo fazer — ele não me ensina o que devo ser. A liberdade exterior só é boa se houver liberdade interior. O mercado pode ser livre, mas se a alma estiver escravizada pelo vício, o colapso será inevitável.
Por isso, não me basta a ética negativa. Creio que uma sociedade justa precisa de valores positivos: honra, responsabilidade, compaixão, respeito, fidelidade à verdade. Sem isso, mesmo uma sociedade que respeite formalmente os direitos individuais apodrecerá por dentro. Um povo que ama o lucro, mas despreza a verdade, que celebra a liberdade mas esquece a justiça, está se preparando para ser dominado. Trocará um déspota visível por mil tiranias invisíveis — o hedonismo, o consumismo, a mentira, o medo.
Não aceito a falsa caridade feita com o dinheiro tomado à força. A verdadeira generosidade nasce do coração livre, não da coerção institucional. Obrigar alguém a ajudar o próximo destrói tanto a liberdade quanto a virtude. Só há mérito onde há escolha. A caridade que nasce do amor é redentora; a que nasce do fisco é propaganda.
O Estado moderno é um ídolo. Ele promete segurança, mas entrega servidão. Promete justiça, mas entrega privilégios. Disfarça a opressão com linguagem técnica, legal e democrática. Mas por trás de suas máscaras, vejo apenas a velha serpente. Um parasita que se alimenta do trabalho alheio e manipula consciências para se perpetuar.
Resistir não é apenas um direito, é um dever. Obedecer a Deus antes que aos homens — essa é a minha regra. O poder se volta contra a verdade, mas minha lealdade pertence a quem criou o céu e a terra. A tirania não se combate com outro tirano, mas com a desobediência firme e pacífica dos que amam a justiça.
Não acredito em utopias. Desejo uma ordem natural, orgânica, enraizada no voluntarismo. Uma sociedade que se construa de baixo para cima: a partir da família, da comunidade local, da tradição e da fé. Não quero uma máquina que planeje a vida alheia, mas um tecido de relações voluntárias onde a liberdade floresça à sombra da cruz.
Desejo, sim, o reinado social de Cristo. Não por imposição, mas por convicção. Que Ele reine nos corações, nas famílias, nas ruas e nos contratos. Que a fé guie a razão e a razão ilumine a vida. Que a liberdade seja meio para a santidade — não um fim em si. E que, livres do jugo do Leviatã, sejamos servos apenas do Senhor.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 30ceb64e:7f08bdf5
2025-04-26 20:33:30
@ 30ceb64e:7f08bdf5
2025-04-26 20:33:30Status: Draft
Author: TheWildHustleAbstract
This NIP defines a framework for storing and sharing health and fitness profile data on Nostr. It establishes a set of standardized event kinds for individual health metrics, allowing applications to selectively access specific health information while preserving user control and privacy.
In this framework exists - NIP-101h.1 Weight using kind 1351 - NIP-101h.2 Height using kind 1352 - NIP-101h.3 Age using kind 1353 - NIP-101h.4 Gender using kind 1354 - NIP-101h.5 Fitness Level using kind 1355
Motivation
I want to build and support an ecosystem of health and fitness related nostr clients that have the ability to share and utilize a bunch of specific interoperable health metrics.
- Selective access - Applications can access only the data they need
- User control - Users can choose which metrics to share
- Interoperability - Different health applications can share data
- Privacy - Sensitive health information can be managed independently
Specification
Kind Number Range
Health profile metrics use the kind number range 1351-1399:
| Kind | Metric | | --------- | ---------------------------------- | | 1351 | Weight | | 1352 | Height | | 1353 | Age | | 1354 | Gender | | 1355 | Fitness Level | | 1356-1399 | Reserved for future health metrics |
Common Structure
All health metric events SHOULD follow these guidelines:
- The content field contains the primary value of the metric
- Required tags:
['t', 'health']- For categorizing as health data['t', metric-specific-tag]- For identifying the specific metric['unit', unit-of-measurement]- When applicable- Optional tags:
['converted_value', value, unit]- For providing alternative unit measurements['timestamp', ISO8601-date]- When the metric was measured['source', application-name]- The source of the measurement
Unit Handling
Health metrics often have multiple ways to be measured. To ensure interoperability:
- Where multiple units are possible, one standard unit SHOULD be chosen as canonical
- When using non-standard units, a
converted_valuetag SHOULD be included with the canonical unit - Both the original and converted values should be provided for maximum compatibility
Client Implementation Guidelines
Clients implementing this NIP SHOULD:
- Allow users to explicitly choose which metrics to publish
- Support reading health metrics from other users when appropriate permissions exist
- Support updating metrics with new values over time
- Preserve tags they don't understand for future compatibility
- Support at least the canonical unit for each metric
Extensions
New health metrics can be proposed as extensions to this NIP using the format:
- NIP-101h.X where X is the metric number
Each extension MUST specify: - A unique kind number in the range 1351-1399 - The content format and meaning - Required and optional tags - Examples of valid events
Privacy Considerations
Health data is sensitive personal information. Clients implementing this NIP SHOULD:
- Make it clear to users when health data is being published
- Consider incorporating NIP-44 encryption for sensitive metrics
- Allow users to selectively share metrics with specific individuals
- Provide easy ways to delete previously published health data
NIP-101h.1: Weight
Description
This NIP defines the format for storing and sharing weight data on Nostr.
Event Kind: 1351
Content
The content field MUST contain the numeric weight value as a string.
Required Tags
- ['unit', 'kg' or 'lb'] - Unit of measurement
- ['t', 'health'] - Categorization tag
- ['t', 'weight'] - Specific metric tag
Optional Tags
- ['converted_value', value, unit] - Provides the weight in alternative units for interoperability
- ['timestamp', ISO8601 date] - When the weight was measured
Examples
json { "kind": 1351, "content": "70", "tags": [ ["unit", "kg"], ["t", "health"], ["t", "weight"] ] }json { "kind": 1351, "content": "154", "tags": [ ["unit", "lb"], ["t", "health"], ["t", "weight"], ["converted_value", "69.85", "kg"] ] }NIP-101h.2: Height
Status: Draft
Description
This NIP defines the format for storing and sharing height data on Nostr.
Event Kind: 1352
Content
The content field can use two formats: - For metric height: A string containing the numeric height value in centimeters (cm) - For imperial height: A JSON string with feet and inches properties
Required Tags
['t', 'health']- Categorization tag['t', 'height']- Specific metric tag['unit', 'cm' or 'imperial']- Unit of measurement
Optional Tags
['converted_value', value, 'cm']- Provides height in centimeters for interoperability when imperial is used['timestamp', ISO8601-date]- When the height was measured
Examples
```jsx // Example 1: Metric height Apply to App.jsx
// Example 2: Imperial height with conversion Apply to App.jsx ```
Implementation Notes
- Centimeters (cm) is the canonical unit for height interoperability
- When using imperial units, a conversion to centimeters SHOULD be provided
- Height values SHOULD be positive integers
- For maximum compatibility, clients SHOULD support both formats
NIP-101h.3: Age
Status: Draft
Description
This NIP defines the format for storing and sharing age data on Nostr.
Event Kind: 1353
Content
The content field MUST contain the numeric age value as a string.
Required Tags
['unit', 'years']- Unit of measurement['t', 'health']- Categorization tag['t', 'age']- Specific metric tag
Optional Tags
['timestamp', ISO8601-date]- When the age was recorded['dob', ISO8601-date]- Date of birth (if the user chooses to share it)
Examples
```jsx // Example 1: Basic age Apply to App.jsx
// Example 2: Age with DOB Apply to App.jsx ```
Implementation Notes
- Age SHOULD be represented as a positive integer
- For privacy reasons, date of birth (dob) is optional
- Clients SHOULD consider updating age automatically if date of birth is known
- Age can be a sensitive metric and clients may want to consider encrypting this data
NIP-101h.4: Gender
Status: Draft
Description
This NIP defines the format for storing and sharing gender data on Nostr.
Event Kind: 1354
Content
The content field contains a string representing the user's gender.
Required Tags
['t', 'health']- Categorization tag['t', 'gender']- Specific metric tag
Optional Tags
['timestamp', ISO8601-date]- When the gender was recorded['preferred_pronouns', string]- User's preferred pronouns
Common Values
While any string value is permitted, the following common values are recommended for interoperability: - male - female - non-binary - other - prefer-not-to-say
Examples
```jsx // Example 1: Basic gender Apply to App.jsx
// Example 2: Gender with pronouns Apply to App.jsx ```
Implementation Notes
- Clients SHOULD allow free-form input for gender
- For maximum compatibility, clients SHOULD support the common values
- Gender is a sensitive personal attribute and clients SHOULD consider appropriate privacy controls
- Applications focusing on health metrics should be respectful of gender diversity
NIP-101h.5: Fitness Level
Status: Draft
Description
This NIP defines the format for storing and sharing fitness level data on Nostr.
Event Kind: 1355
Content
The content field contains a string representing the user's fitness level.
Required Tags
['t', 'health']- Categorization tag['t', 'fitness']- Fitness category tag['t', 'level']- Specific metric tag
Optional Tags
['timestamp', ISO8601-date]- When the fitness level was recorded['activity', activity-type]- Specific activity the fitness level relates to['metrics', JSON-string]- Quantifiable fitness metrics used to determine level
Common Values
While any string value is permitted, the following common values are recommended for interoperability: - beginner - intermediate - advanced - elite - professional
Examples
```jsx // Example 1: Basic fitness level Apply to App.jsx
// Example 2: Activity-specific fitness level with metrics Apply to App.jsx ```
Implementation Notes
- Fitness level is subjective and may vary by activity
- The activity tag can be used to specify fitness level for different activities
- The metrics tag can provide objective measurements to support the fitness level
- Clients can extend this format to include activity-specific fitness assessments
- For general fitness apps, the simple beginner/intermediate/advanced scale is recommended
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 8125b911:a8400883
2025-04-25 07:02:35
@ 8125b911:a8400883
2025-04-25 07:02:35In Nostr, all data is stored as events. Decentralization is achieved by storing events on multiple relays, with signatures proving the ownership of these events. However, if you truly want to own your events, you should run your own relay to store them. Otherwise, if the relays you use fail or intentionally delete your events, you'll lose them forever.
For most people, running a relay is complex and costly. To solve this issue, I developed nostr-relay-tray, a relay that can be easily run on a personal computer and accessed over the internet.
Project URL: https://github.com/CodyTseng/nostr-relay-tray
This article will guide you through using nostr-relay-tray to run your own relay.
Download
Download the installation package for your operating system from the GitHub Release Page.
| Operating System | File Format | | --------------------- | ---------------------------------- | | Windows |
nostr-relay-tray.Setup.x.x.x.exe| | macOS (Apple Silicon) |nostr-relay-tray-x.x.x-arm64.dmg| | macOS (Intel) |nostr-relay-tray-x.x.x.dmg| | Linux | You should know which one to use |Installation
Since this app isn’t signed, you may encounter some obstacles during installation. Once installed, an ostrich icon will appear in the status bar. Click on the ostrich icon, and you'll see a menu where you can click the "Dashboard" option to open the relay's control panel for further configuration.

macOS Users:
- On first launch, go to "System Preferences > Security & Privacy" and click "Open Anyway."
- If you encounter a "damaged" message, run the following command in the terminal to remove the restrictions:
bash sudo xattr -rd com.apple.quarantine /Applications/nostr-relay-tray.appWindows Users:
- On the security warning screen, click "More Info > Run Anyway."
Connecting
By default, nostr-relay-tray is only accessible locally through
ws://localhost:4869/, which makes it quite limited. Therefore, we need to expose it to the internet.In the control panel, click the "Proxy" tab and toggle the switch. You will then receive a "Public address" that you can use to access your relay from anywhere. It's that simple.
Next, add this address to your relay list and position it as high as possible in the list. Most clients prioritize connecting to relays that appear at the top of the list, and relays lower in the list are often ignored.

Restrictions
Next, we need to set up some restrictions to prevent the relay from storing events that are irrelevant to you and wasting storage space. nostr-relay-tray allows for flexible and fine-grained configuration of which events to accept, but some of this is more complex and will not be covered here. If you're interested, you can explore this further later.
For now, I'll introduce a simple and effective strategy: WoT (Web of Trust). You can enable this feature in the "WoT & PoW" tab. Before enabling, you'll need to input your pubkey.
There's another important parameter,
Depth, which represents the relationship depth between you and others. Someone you follow has a depth of 1, someone they follow has a depth of 2, and so on.- Setting this parameter to 0 means your relay will only accept your own events.
- Setting it to 1 means your relay will accept events from you and the people you follow.
- Setting it to 2 means your relay will accept events from you, the people you follow, and the people they follow.
Currently, the maximum value for this parameter is 2.

Conclusion
You've now successfully run your own relay and set a simple restriction to prevent it from storing irrelevant events.
If you encounter any issues during use, feel free to submit an issue on GitHub, and I'll respond as soon as possible.
Not your relay, not your events.
-
 @ 5df413d4:2add4f5b
2025-05-13 12:37:20
@ 5df413d4:2add4f5b
2025-05-13 12:37:20https://i.nostr.build/Ur1Je684aSgYCRn3.jpg
You Are Not A Gadget by Jaron Lanier
Reading Jaron Lanier’s 2010 You Are Not A Gadget in 2023 is an interesting experience—equal parts withering, prophetic, and heretical clarion call warning from a high priest of the Technocracy and rambling, musing, cognitive jam session from a technofied musician-philosopher.
Yet, in ways that I think the author would be simultaneously pleased, amused, saddened, and disturbed by, the 13 yeas since the book’s publishing have, in places, proven him right with stunning foresight and precision, and in others, made his ideas appear laughable, bizarre, even naive. The book is written in five parts, yet I would suggest viewing it as two discrete elements—Part One (around the first half of the book) and…everything else.
For context, Lanier, is a computer scientist and early technologist from the area of Jobs, Wozniak, and Gates, and is considered to be a founding father of virtual reality. He is also a consummate contrarian, a player of rare and obscure musical instruments, a deep interdisciplinary thinker…and a white man with dreadlocks named Jaron.
PART ONE
Part One of the book “What is a Person?” reads like a scathing and clear-eye manifesto—where Lanier is batting 1000, merciless in his rightness. Were one to pull a passage that speaks to the soul of this portion of the book, it might be the following: “The net does not design itself. We design it.”
Lanier terms the prevailing technocratic ideology—the particular winning tech-nerd subculture that has now come to capture our society—as “the cybernetic totalist” or “digital Maoists.” Essentially a materialist and stealth collectivist movement in new-age technocratic dress, that through its successes, and now excesses, represents much the same of religion that it’s founders would have claimed to be “evolving past.”
Lanier points out that in this, we are simply trading the pursuit of finding God in spirituality or the afterlife, for a notion of digital immortality—seeking, or, if possible, becoming, God in the cloud. He aptly identifies that this worldview requires that society, and all human interactions really, be savagely bent into adherence to this new religion of aggregation that demands deification of data, gross diminishment of the individual, and belief in some objective (but never defined) "meaning" that exists beyond and apart from the human observer.
With skill and simple wit, he raises strong, rational counterpoint to the digital Maoists’ obsession with quantity, data in aggregate and at-scale, as society's prime directive “A fashionable idea in technical circles is that quantity […] turns into quality at some extreme scale […] I disagree. A trope in the early days or computer science comes to mind: garbage in, garbage out.”
Lanier is able to envision the digital cages that likes of Facebook, Youtube, social-media dating apps would become for the internet native generations. Of whom he writes “The most effective young Facebook users […] are the ones who create successful online fictions about themselves,” and “If you start out by being fake, you’ll eventually have to put in twice the effort to undo the illusion if anything good is to come of it.”
Lanier’s 2010 criticism of Wikipedia-ism is now double or triply apropos in our current hype cycle of “AI magic” and Everything-GPT, “Wikipedia, for instance, works on what I can the Oracle Illusion, in which knowledge of human authorship of a text is suppressed in order to give the text superhuman validity. Traditional holy books work in precisely the same way and present many of the same problems.” This same deep truth now sits at the heart of every “new” creation churned out by the flavor-of-the-week, plagiarism-at-scale, generative AI tool.
More darkly, he is also able to foresee the spectre of a return to collectivism lurking both at the core and on the margins of our new digital age—“The recipe that led to social catastrophe in the past was economic humiliation combined with collectivist ideology. We already have the ideology in its new digital packaging, and it’s entirely possible we could face dangerously traumatic economic shock in the coming decades.”—“No Shit” said everyone who lived through 2020-2022…
This brings us, eerily, to the world of today. Where aggregate insights are upheld as more valuable than discrete insights. Where crowds are are assumed to have more wisdom than individuals. Where truth is twisted into a might-is-right numbers game. A world ruled by the idea that if we can just centralize enough information and sufficiently pulverize authorship, the result will, necessarily, be something super-intelligent, "alive," and perhaps even divine.
In short, the cybernetic totalists and digital Maoists, having killed reason, now sit on its corpse like a thrown, smearing its blood on the walls in the name of art and reading its still-steaming entrails for prophecy.
If I were to infer some ideological takeaway from Part One of the book, it might be that Lanier seems to axiomatically reject any affirmative implication of the Turing Test. Simply put, he believes that bits are not and cannot ever be alive independent of the human-as-oracle. Further, there is no objective meaning beyond the human observer—in fact, that observer fundamentally creates any meaning there is to be had. This is best illustrated by one of the most powerful passages in the book:
“But the Turing Test cuts both ways. You can’t tell if a machine has gotten smarter or if you’ve just lowered your own standard of intelligence to such a degree that the machine seems smart. If you can have a conversation with a simulated person presented by an AI program, can you tell how far you’ve let your sense of personhood degrade in order to make the illusion work for you?”
Ponder this well, Anon.
EVERYTHING ELSE
With all of the great stuff above out of the way, we must turn to…the rest of the book. Parts Two through Five breakdown into something more like a stream of consciousness. And while there are certainly many nuggets to insight and beauty to be found, the book becomes largely dis-coherent and very difficult to read. That said, the remainder of the book does contain three particularly compelling threads that I find to be worth pulling on.
Internet Attribution First, are Lanier’s musing about money and attribution in our authorless “information wants to be free” world. He laments the infinite elevation of advertising and offers harsh critique to the concept of attention as the new currency—as this tends to overwhelmingly reward the aggregator and a piddling few soulless super-influencers at the expense of all other users and creators.
Interestingly, under the guise of “what could have been” he imagines a world where attribution is tracked across the web (though how this achieved is left unanswered) and royalty payments can flow back to the author seamlessly over the internet. I find his vision to be intriguing because in 2010, we lacked the technology to either track attribution across the web or facilitate seamless micropayment royalties based on access / usage.
While we still don't have the ability to achieve the type of fully-tracked, always-on attribution Lanier imagines, we do now have the ability to stream payments across the internet with bitcoin and the lightning network. While Lanier can be excused for not mentioning the then uber-nascent bitcoin in 2010, bitcoin’s development since only goes to underscore the prescience of Lanier’s imagination.
The bigger question that now remains, especially in the face of the advent of “AI,” is whether such a system to manage and therefore enforce attribution globally on the internet would even be a good thing. Where obscured attribution enables mashed-up plagiarism-at-scale, centrally enforced attribution can just as easily enable idea, content, discovery, and innovation suppression-at-scale.
Music in the New Age Second, much of the book, particularly in the second half, is filtered through the lens and language of music. Music is essential to Lanier’s inner life and it is clear that he views music as an emergent mystery force attributable to something unknowable, if not divine, and entirely unique to the human experience.
He bemoans the music of the 2000s as lacking in any distinct chronological era sound—everything is either a rehashed mashup or digitally lofi-ed emulation of sounds from previous begone eras—it is music that is impossible to place. To him, it is as though musical evolution stopped right around the time of the advent of the internet…and then folded back in on itself, creating an endless kaleidoscoping of what came before but rarely, if ever, the creation anything truly new.
In response, Lanier goes so far as to imagine the ridiculous (my take, not his) world of “Songles”—songs on dongles—essentially physical music NFTs. In Songleland, listening to the hottest tracks at a party hinges on the guy or gal with the dankest songles swinging through and plugging them into the Songle player. And songles, being scarce, even become speculative investments. On this, Lanier manages to be both right and wrong in only the most spectacularly absurd of ways.
But what Lanier really laments is the passing of popular music as a shared cultural experience at national or even global scale. During Lanier’s coming of age through the 1960-80s—with only a few consolidated channels for music distribution, it was truly impossible to escape the sounds and influence of the Beatles or Prince or Micheal Jackson—everyone heard it and even the deaf still felt it.
In the end, Lanier could image Songles but he couldn’t envision what Spotify would become—a conduit to shatter music distribution into a myriad of tiny longtails—providing infinitely fragmented and individually fine-tuned music experiences rather than large and cohesive cultural moments. However, even in this miss, Lanier is largely able to project what Spotify-ed music would resolve to—music designed as much or more to please the self-referential selection algorithm than any real, human listeners. A dangerously foretelling insight that goes well beyond music as AI tools are posed to become the "googling" of the next technological cycle—what happens to information, to human thought, when the majority of "generative AI" outputs are just the machine referencing itself?
Digital Neoteny The final thread to pull is that of "digital neoteny," the retention of juvenile behaviors in adult form, in this case, a neoteny of the mind if you will. Lanier sees the internet as specifically primed to propagate three kinds of neoteny in digital-native humans— a blissful and curious Bachelardian neoteny (as in Gaston Bachelard’s Poetics of Reverie); a cruel and mob-like Goldingesque neoteny (as in William Golding’s Lord of the Flies); and a general and deeply pervasive, infantile neoteny.
Neoteny of the Bachelardian variety, which Lanier likens to “the sense of wonder and weirdness that a teen can find in the unfolding world,” is what he feels the internet has provided in a few brief and magical moments generally aligned with the “early days” of successive internet technologies, movements, and companies—through this generally degrades into Goldingesque neoteny as novelty gives way to ossification.
Lanier’s missives on Bachelardian neoteny feel especially pertinent to the present state of Nostr (where I am publishing this writing). Nostr is in a moment where winner-take all dynamics and corporatization have yet to take hold. Child-like revelry abounds with each new discovery or novel Nostr client development so much so that the likes of Jack Dorsey compare it to the excitement of the early internet.
But with time, if and as the Nostr protocol wins, to what extent will technical lock-in take hold here? To what extent will calcification of seemingly trivial or even comical decisions being made by client devs today have dramatic implications on the feasibility of other development in the future? And will we early Nostr users, at some point put down welcoming inclusivesness for insular tribalism—and in what ways might we be doing this already?
Finally, to the third kind of neoteny, Infantile neoteny—which perhaps incapsulates the internet even more so than either of the other two types—Lanier sees the net driving an evermore prolonged deferral of maturity, resulting ultimately in some centrally-managed permanent arresting of society in a stupefied and juvenile mental state:
“Some of the greatest speculative investments in human history continue to converge on Silicon Valley schemes that seemed to have been named by Dr. Seuss. On any given day, one might hear of tens or hundreds of millions of dollars flowing to a start-up company named Ublibudly or MeTickly. These are names I just made up, but they would make great venture capital bait if they existed. At these companies one finds rooms full of MIT PhD engineers not seeking cancer cures or sources of safe drinking water for the underdeveloped world but schemes to send little digital pictures of teddy bears and dragons between adult members of social networks. At the end of the road of the pursuit of technological sophistication appears to lie a playhouse in which humankind regresses to nursery school.”
The popular culture of the early 2020s—with it’s NFT Monke JPEGs, silent and masked TikTok dancing in the drab aisles of crumbling department stores, and rampant peer-pressured social-media virtue-signaling and paternalism—could scarcely be described in any more stark and specific detail. That such could be seen so vividly in 2010 is as masterful as it is dishearteningly dark.
CONCLUSION
You Are Not A Gadget is a special thing, a strange beast—as lucid in its first half as it is jumbled, meandering, and even nonsensical in its second half. And while the discerning reader might judge the book harshly for these structural failings, I doubt the author would care, he might even welcome it. Lanier’s apparent purpose in writing is to share his mind rather than please the reader in any particular regard. The sufficiently curious reader, one who is willing to engage with the book’s content, for whatever the book’s faults may be, finds a king’s randoms of wisdom, insight, and uncanny foresight.
In closing, it seems fitting to recall one of Lanier’s earliest warnings in the book, “Maybe if people pretend they are not conscious or do not have free will […] then perhaps we have the power to make it so. We might be able to collectively achieve antimagic.” 13 years on, this feels more pressing and urgent and true than ever. (Rating: 4/5🐙)
~Moon
Buy the Book: You Are Not A Gadget
-
 @ e691f4df:1099ad65
2025-04-24 18:56:12
@ e691f4df:1099ad65
2025-04-24 18:56:12Viewing Bitcoin Through the Light of Awakening
Ankh & Ohm Capital’s Overview of the Psycho-Spiritual Nature of Bitcoin
Glossary:
I. Preface: The Logos of Our Logo
II. An Oracular Introduction
III. Alchemizing Greed
IV. Layers of Fractalized Thought
V. Permissionless Individuation
VI. Dispelling Paradox Through Resonance
VII. Ego Deflation
VIII. The Coin of Great Price
Preface: The Logos of Our Logo
Before we offer our lens on Bitcoin, it’s important to illuminate the meaning behind Ankh & Ohm’s name and symbol. These elements are not ornamental—they are foundational, expressing the cosmological principles that guide our work.
Our mission is to bridge the eternal with the practical. As a Bitcoin-focused family office and consulting firm, we understand capital not as an end, but as a tool—one that, when properly aligned, becomes a vehicle for divine order. We see Bitcoin not simply as a technological innovation but as an emanation of the Divine Logos—a harmonic expression of truth, transparency, and incorruptible structure. Both the beginning and the end, the Alpha and Omega.
The Ankh (☥), an ancient symbol of eternal life, is a key to the integration of opposites. It unites spirit and matter, force and form, continuity and change. It reminds us that capital, like Life, must not only be generative, but regenerative; sacred. Money must serve Life, not siphon from it.
The Ohm (Ω) holds a dual meaning. In physics, it denotes a unit of electrical resistance—the formative tension that gives energy coherence. In the Vedic tradition, Om (ॐ) is the primordial vibration—the sound from which all existence unfolds. Together, these symbols affirm a timeless truth: resistance and resonance are both sacred instruments of the Creator.
Ankh & Ohm, then, represents our striving for union, for harmony —between the flow of life and intentional structure, between incalculable abundance and measured restraint, between the lightbulb’s electrical impulse and its light-emitting filament. We stand at the threshold where intention becomes action, and where capital is not extracted, but cultivated in rhythm with the cosmos.
We exist to shepherd this transformation, as guides of this threshold —helping families, founders, and institutions align with a deeper order, where capital serves not as the prize, but as a pathway to collective Presence, Purpose, Peace and Prosperity.
An Oracular Introduction
Bitcoin is commonly understood as the first truly decentralized and secure form of digital money—a breakthrough in monetary sovereignty. But this view, while technically correct, is incomplete and spiritually shallow. Bitcoin is more than a tool for economic disruption. Bitcoin represents a mythic threshold: a symbol of the psycho-spiritual shift that many ancient traditions have long foretold.
For millennia, sages and seers have spoken of a coming Golden Age. In the Vedic Yuga cycles, in Plato’s Great Year, in the Eagle and Condor prophecies of the Americas—there exists a common thread: that humanity will emerge from darkness into a time of harmony, cooperation, and clarity. That the veil of illusion (maya, materiality) will thin, and reality will once again become transparent to the transcendent. In such an age, systems based on scarcity, deception, and centralization fall away. A new cosmology takes root—one grounded in balance, coherence, and sacred reciprocity.
But we must ask—how does such a shift happen? How do we cross from the age of scarcity, fear, and domination into one of coherence, abundance, and freedom?
One possible answer lies in the alchemy of incentive.
Bitcoin operates not just on the rules of computer science or Austrian economics, but on something far more old and subtle: the logic of transformation. It transmutes greed—a base instinct rooted in scarcity—into cooperation, transparency, and incorruptibility.
In this light, Bitcoin becomes more than code—it becomes a psychoactive protocol, one that rewires human behavior by aligning individual gain with collective integrity. It is not simply a new form of money. It is a new myth of value. A new operating system for human consciousness.
Bitcoin does not moralize. It harmonizes. It transforms the instinct for self-preservation into a pathway for planetary coherence.
Alchemizing Greed
At the heart of Bitcoin lies the ancient alchemical principle of transmutation: that which is base may be refined into gold.
Greed, long condemned as a vice, is not inherently evil. It is a distorted longing. A warped echo of the drive to preserve life. But in systems built on scarcity and deception, this longing calcifies into hoarding, corruption, and decay.
Bitcoin introduces a new game. A game with memory. A game that makes deception inefficient and truth profitable. It does not demand virtue—it encodes consequence. Its design does not suppress greed; it reprograms it.
In traditional models, game theory often illustrates the fragility of trust. The Prisoner’s Dilemma reveals how self-interest can sabotage collective well-being. But Bitcoin inverts this. It creates an environment where self-interest and integrity converge—where the most rational action is also the most truthful.
Its ledger, immutable and transparent, exposes manipulation for what it is: energetically wasteful and economically self-defeating. Dishonesty burns energy and yields nothing. The network punishes incoherence, not by decree, but by natural law.
This is the spiritual elegance of Bitcoin: it does not suppress greed—it transmutes it. It channels the drive for personal gain into the architecture of collective order. Miners compete not to dominate, but to validate. Nodes collaborate not through trust, but through mathematical proof.
This is not austerity. It is alchemy.
Greed, under Bitcoin, is refined. Tempered. Re-forged into a generative force—no longer parasitic, but harmonic.
Layers of Fractalized Thought Fragments
All living systems are layered. So is the cosmos. So is the human being. So is a musical scale.
At its foundation lies the timechain—the pulsing, incorruptible record of truth. Like the heart, it beats steadily. Every block, like a pulse, affirms its life through continuity. The difficulty adjustment—Bitcoin’s internal calibration—functions like heart rate variability, adapting to pressure while preserving coherence.
Above this base layer is the Lightning Network—a second layer facilitating rapid, efficient transactions. It is the nervous system: transmitting energy, reducing latency, enabling real-time interaction across a distributed whole.
Beyond that, emerging tools like Fedimint and Cashu function like the capillaries—bringing vitality to the extremities, to those underserved by legacy systems. They empower the unbanked, the overlooked, the forgotten. Privacy and dignity in the palms of those the old system refused to see.
And then there is NOSTR—the decentralized protocol for communication and creation. It is the throat chakra, the vocal cords of the “freedom-tech” body. It reclaims speech from the algorithmic overlords, making expression sovereign once more. It is also the reproductive system, as it enables the propagation of novel ideas and protocols in fertile, uncensorable soil.
Each layer plays its part. Not in hierarchy, but in harmony. In holarchy. Bitcoin and other open source protocols grow not through exogenous command, but through endogenous coherence. Like cells in an organism. Like a song.
Imagine the cell as a piece of glass from a shattered holographic plate —by which its perspectival, moving image can be restructured from the single shard. DNA isn’t only a logical script of base pairs, but an evolving progressive song. Its lyrics imbued with wise reflections on relationships. The nucleus sings, the cell responds—not by command, but by memory. Life is not imposed; it is expressed. A reflection of a hidden pattern.
Bitcoin chants this. Each node, a living cell, holds the full timechain—Truth distributed, incorruptible. Remove one, and the whole remains. This isn’t redundancy. It’s a revelation on the power of protection in Truth.
Consensus is communion. Verification becomes a sacred rite—Truth made audible through math.
Not just the signal; the song. A web of self-expression woven from Truth.
No center, yet every point alive with the whole. Like Indra’s Net, each reflects all. This is more than currency and information exchange. It is memory; a self-remembering Mind, unfolding through consensus and code. A Mind reflecting the Truth of reality at the speed of thought.
Heuristics are mental shortcuts—efficient, imperfect, alive. Like cells, they must adapt or decay. To become unbiased is to have self-balancing heuristics which carry feedback loops within them: they listen to the environment, mutate when needed, and survive by resonance with reality. Mutation is not error, but evolution. Its rules are simple, but their expression is dynamic.
What persists is not rigidity, but pattern.
To think clearly is not necessarily to be certain, but to dissolve doubt by listening, adjusting, and evolving thought itself.
To understand Bitcoin is simply to listen—patiently, clearly, as one would to a familiar rhythm returning.
Permissionless Individuation
Bitcoin is a path. One that no one can walk for you.
Said differently, it is not a passive act. It cannot be spoon-fed. Like a spiritual path, it demands initiation, effort, and the willingness to question inherited beliefs.
Because Bitcoin is permissionless, no one can be forced to adopt it. One must choose to engage it—compelled by need, interest, or intuition. Each person who embarks undergoes their own version of the hero’s journey.
Carl Jung called this process Individuation—the reconciliation of fragmented psychic elements into a coherent, mature Self. Bitcoin mirrors this: it invites individuals to confront the unconscious assumptions of the fiat paradigm, and to re-integrate their relationship to time, value, and agency.
In Western traditions—alchemy, Christianity, Kabbalah—the individual is sacred, and salvation is personal. In Eastern systems—Daoism, Buddhism, the Vedas—the self is ultimately dissolved into the cosmic whole. Bitcoin, in a paradoxical way, echoes both: it empowers the individual, while aligning them with a holistic, transcendent order.
To truly see Bitcoin is to allow something false to die. A belief. A habit. A self-concept.
In that death—a space opens for deeper connection with the Divine itSelf.
In that dissolution, something luminous is reborn.
After the passing, Truth becomes resurrected.
Dispelling Paradox Through Resonance
There is a subtle paradox encoded into the hero’s journey: each starts in solidarity, yet the awakening affects the collective.
No one can be forced into understanding Bitcoin. Like a spiritual truth, it must be seen. And yet, once seen, it becomes nearly impossible to unsee—and easier for others to glimpse. The pattern catches.
This phenomenon mirrors the concept of morphic resonance, as proposed and empirically tested by biologist Rupert Sheldrake. Once a critical mass of individuals begins to embody a new behavior or awareness, it becomes easier—instinctive—for others to follow suit. Like the proverbial hundredth monkey who begins to wash the fruit in the sea water, and suddenly, monkeys across islands begin doing the same—without ever meeting.
When enough individuals embody a pattern, it ripples outward. Not through propaganda, but through field effect and wave propagation. It becomes accessible, instinctive, familiar—even across great distance.
Bitcoin spreads in this way. Not through centralized broadcast, but through subtle resonance. Each new node, each individual who integrates the protocol into their life, strengthens the signal for others. The protocol doesn’t shout; it hums, oscillates and vibrates——persistently, coherently, patiently.
One awakens. Another follows. The current builds. What was fringe becomes familiar. What was radical becomes obvious.
This is the sacred geometry of spiritual awakening. One awakens, another follows, and soon the fluidic current is strong enough to carry the rest. One becomes two, two become many, and eventually the many become One again. This tessellation reverberates through the human aura, not as ideology, but as perceivable pattern recognition.
Bitcoin’s most powerful marketing tool is truth. Its most compelling evangelist is reality. Its most unstoppable force is resonance.
Therefore, Bitcoin is not just financial infrastructure—it is psychic scaffolding. It is part of the subtle architecture through which new patterns of coherence ripple across the collective field.
The training wheels from which humanity learns to embody Peace and Prosperity.
Ego Deflation
The process of awakening is not linear, and its beginning is rarely gentle—it usually begins with disruption, with ego inflation and destruction.
To individuate is to shape a center; to recognize peripherals and create boundaries—to say, “I am.” But without integration, the ego tilts—collapsing into void or inflating into noise. Fiat reflects this pathology: scarcity hoarded, abundance simulated. Stagnation becomes disguised as safety, and inflation masquerades as growth.
In other words, to become whole, the ego must first rise—claiming agency, autonomy, and identity. However, when left unbalanced, it inflates, or implodes. It forgets its context. It begins to consume rather than connect. And so the process must reverse: what inflates must deflate.
In the fiat paradigm, this inflation is literal. More is printed, and ethos is diluted. Savings decay. Meaning erodes. Value is abstracted. The economy becomes bloated with inaudible noise. And like the psyche that refuses to confront its own shadow, it begins to collapse under the weight of its own illusions.
But under Bitcoin, time is honored. Value is preserved. Energy is not abstracted but grounded.
Bitcoin is inherently deflationary—in both economic and spiritual senses. With a fixed supply, it reveals what is truly scarce. Not money, not status—but the finite number of heartbeats we each carry.
To see Bitcoin is to feel that limit in one’s soul. To hold Bitcoin is to feel Time’s weight again. To sense the importance of Bitcoin is to feel the value of preserved, potential energy. It is to confront the reality that what matters cannot be printed, inflated, or faked. In this way, Bitcoin gently confronts the ego—not through punishment, but through clarity.
Deflation, rightly understood, is not collapse—it is refinement. It strips away illusion, bloat, and excess. It restores the clarity of essence.
Spiritually, this is liberation.
The Coin of Great Price
There is an ancient parable told by a wise man:
“The kingdom of heaven is like a merchant seeking fine pearls, who, upon finding one of great price, sold all he had and bought it.”
Bitcoin is such a pearl.
But the ledger is more than a chest full of treasure. It is a key to the heart of things.
It is not just software—it is sacrament.
A symbol of what cannot be corrupted. A mirror of divine order etched into code. A map back to the sacred center.
It reflects what endures. It encodes what cannot be falsified. It remembers what we forgot: that Truth, when aligned with form, becomes Light once again.
Its design is not arbitrary. It speaks the language of life itself—
The elliptic orbits of the planets mirrored in its cryptography,
The logarithmic spiral of the nautilus shell discloses its adoption rate,
The interconnectivity of mycelium in soil reflect the network of nodes in cyberspace,
A webbed breadth of neurons across synaptic space fires with each new confirmed transaction.
It is geometry in devotion. Stillness in motion.
It is the Logos clothed in protocol.
What this key unlocks is beyond external riches. It is the eternal gold within us.
Clarity. Sovereignty. The unshakeable knowing that what is real cannot be taken. That what is sacred was never for sale.
Bitcoin is not the destination.
It is the Path.
And we—when we are willing to see it—are the Temple it leads back to.
-
 @ 40b9c85f:5e61b451
2025-04-24 15:27:02
@ 40b9c85f:5e61b451
2025-04-24 15:27:02Introduction
Data Vending Machines (DVMs) have emerged as a crucial component of the Nostr ecosystem, offering specialized computational services to clients across the network. As defined in NIP-90, DVMs operate on an apparently simple principle: "data in, data out." They provide a marketplace for data processing where users request specific jobs (like text translation, content recommendation, or AI text generation)
While DVMs have gained significant traction, the current specification faces challenges that hinder widespread adoption and consistent implementation. This article explores some ideas on how we can apply the reflection pattern, a well established approach in RPC systems, to address these challenges and improve the DVM ecosystem's clarity, consistency, and usability.
The Current State of DVMs: Challenges and Limitations
The NIP-90 specification provides a broad framework for DVMs, but this flexibility has led to several issues:
1. Inconsistent Implementation
As noted by hzrd149 in "DVMs were a mistake" every DVM implementation tends to expect inputs in slightly different formats, even while ostensibly following the same specification. For example, a translation request DVM might expect an event ID in one particular format, while an LLM service could expect a "prompt" input that's not even specified in NIP-90.
2. Fragmented Specifications
The DVM specification reserves a range of event kinds (5000-6000), each meant for different types of computational jobs. While creating sub-specifications for each job type is being explored as a possible solution for clarity, in a decentralized and permissionless landscape like Nostr, relying solely on specification enforcement won't be effective for creating a healthy ecosystem. A more comprehensible approach is needed that works with, rather than against, the open nature of the protocol.
3. Ambiguous API Interfaces
There's no standardized way for clients to discover what parameters a specific DVM accepts, which are required versus optional, or what output format to expect. This creates uncertainty and forces developers to rely on documentation outside the protocol itself, if such documentation exists at all.
The Reflection Pattern: A Solution from RPC Systems
The reflection pattern in RPC systems offers a compelling solution to many of these challenges. At its core, reflection enables servers to provide metadata about their available services, methods, and data types at runtime, allowing clients to dynamically discover and interact with the server's API.
In established RPC frameworks like gRPC, reflection serves as a self-describing mechanism where services expose their interface definitions and requirements. In MCP reflection is used to expose the capabilities of the server, such as tools, resources, and prompts. Clients can learn about available capabilities without prior knowledge, and systems can adapt to changes without requiring rebuilds or redeployments. This standardized introspection creates a unified way to query service metadata, making tools like
grpcurlpossible without requiring precompiled stubs.How Reflection Could Transform the DVM Specification
By incorporating reflection principles into the DVM specification, we could create a more coherent and predictable ecosystem. DVMs already implement some sort of reflection through the use of 'nip90params', which allow clients to discover some parameters, constraints, and features of the DVMs, such as whether they accept encryption, nutzaps, etc. However, this approach could be expanded to provide more comprehensive self-description capabilities.
1. Defined Lifecycle Phases
Similar to the Model Context Protocol (MCP), DVMs could benefit from a clear lifecycle consisting of an initialization phase and an operation phase. During initialization, the client and DVM would negotiate capabilities and exchange metadata, with the DVM providing a JSON schema containing its input requirements. nip-89 (or other) announcements can be used to bootstrap the discovery and negotiation process by providing the input schema directly. Then, during the operation phase, the client would interact with the DVM according to the negotiated schema and parameters.
2. Schema-Based Interactions
Rather than relying on rigid specifications for each job type, DVMs could self-advertise their schemas. This would allow clients to understand which parameters are required versus optional, what type validation should occur for inputs, what output formats to expect, and what payment flows are supported. By internalizing the input schema of the DVMs they wish to consume, clients gain clarity on how to interact effectively.
3. Capability Negotiation
Capability negotiation would enable DVMs to advertise their supported features, such as encryption methods, payment options, or specialized functionalities. This would allow clients to adjust their interaction approach based on the specific capabilities of each DVM they encounter.
Implementation Approach
While building DVMCP, I realized that the RPC reflection pattern used there could be beneficial for constructing DVMs in general. Since DVMs already follow an RPC style for their operation, and reflection is a natural extension of this approach, it could significantly enhance and clarify the DVM specification.
A reflection enhanced DVM protocol could work as follows: 1. Discovery: Clients discover DVMs through existing NIP-89 application handlers, input schemas could also be advertised in nip-89 announcements, making the second step unnecessary. 2. Schema Request: Clients request the DVM's input schema for the specific job type they're interested in 3. Validation: Clients validate their request against the provided schema before submission 4. Operation: The job proceeds through the standard NIP-90 flow, but with clearer expectations on both sides
Parallels with Other Protocols
This approach has proven successful in other contexts. The Model Context Protocol (MCP) implements a similar lifecycle with capability negotiation during initialization, allowing any client to communicate with any server as long as they adhere to the base protocol. MCP and DVM protocols share fundamental similarities, both aim to expose and consume computational resources through a JSON-RPC-like interface, albeit with specific differences.
gRPC's reflection service similarly allows clients to discover service definitions at runtime, enabling generic tools to work with any gRPC service without prior knowledge. In the REST API world, OpenAPI/Swagger specifications document interfaces in a way that makes them discoverable and testable.
DVMs would benefit from adopting these patterns while maintaining the decentralized, permissionless nature of Nostr.
Conclusion
I am not attempting to rewrite the DVM specification; rather, explore some ideas that could help the ecosystem improve incrementally, reducing fragmentation and making the ecosystem more comprehensible. By allowing DVMs to self describe their interfaces, we could maintain the flexibility that makes Nostr powerful while providing the structure needed for interoperability.
For developers building DVM clients or libraries, this approach would simplify consumption by providing clear expectations about inputs and outputs. For DVM operators, it would establish a standard way to communicate their service's requirements without relying on external documentation.
I am currently developing DVMCP following these patterns. Of course, DVMs and MCP servers have different details; MCP includes capabilities such as tools, resources, and prompts on the server side, as well as 'roots' and 'sampling' on the client side, creating a bidirectional way to consume capabilities. In contrast, DVMs typically function similarly to MCP tools, where you call a DVM with an input and receive an output, with each job type representing a different categorization of the work performed.
Without further ado, I hope this article has provided some insight into the potential benefits of applying the reflection pattern to the DVM specification.
-
 @ 6e64b83c:94102ee8
2025-04-23 20:23:34
@ 6e64b83c:94102ee8
2025-04-23 20:23:34How to Run Your Own Nostr Relay on Android with Cloudflare Domain
Prerequisites
- Install Citrine on your Android device:
- Visit https://github.com/greenart7c3/Citrine/releases
- Download the latest release using:
- zap.store
- Obtainium
- F-Droid
- Or download the APK directly
-
Note: You may need to enable "Install from Unknown Sources" in your Android settings
-
Domain Requirements:
- Purchase a domain if you don't have one
-
Transfer your domain to Cloudflare if it's not already there (for free SSL certificates and cloudflared support)
-
Tools to use:
- nak (the nostr army knife):
- Download from https://github.com/fiatjaf/nak/releases
- Installation steps:
-
For Linux/macOS: ```bash # Download the appropriate version for your system wget https://github.com/fiatjaf/nak/releases/latest/download/nak-linux-amd64 # for Linux # or wget https://github.com/fiatjaf/nak/releases/latest/download/nak-darwin-amd64 # for macOS
# Make it executable chmod +x nak-*
# Move to a directory in your PATH sudo mv nak-* /usr/local/bin/nak
- For Windows:batch # Download the Windows version curl -L -o nak.exe https://github.com/fiatjaf/nak/releases/latest/download/nak-windows-amd64.exe# Move to a directory in your PATH (e.g., C:\Windows) move nak.exe C:\Windows\nak.exe
- Verify installation:bash nak --version ```
Setting Up Citrine
- Open the Citrine app
- Start the server
- You'll see it running on
ws://127.0.0.1:4869(local network only) - Go to settings and paste your npub into "Accept events signed by" inbox and press the + button. This prevents others from publishing events to your personal relay.
Installing Required Tools
- Install Termux from Google Play Store
- Open Termux and run:
bash pkg update && pkg install wget wget https://github.com/cloudflare/cloudflared/releases/latest/download/cloudflared-linux-arm64.deb dpkg -i cloudflared-linux-arm64.debCloudflare Authentication
- Run the authentication command:
bash cloudflared tunnel login - Follow the instructions:
- Copy the provided URL to your browser
- Log in to your Cloudflare account
- If the URL expires, copy it again after logging in
Creating the Tunnel
- Create a new tunnel:
bash cloudflared tunnel create <TUNNEL_NAME> - Choose any name you prefer for your tunnel
-
Copy the tunnel ID after creating the tunnel
-
Create and configure the tunnel config:
bash touch ~/.cloudflared/config.yml nano ~/.cloudflared/config.yml -
Add this configuration (replace the placeholders with your values): ```yaml tunnel:
credentials-file: /data/data/com.termux/files/home/.cloudflared/ .json ingress: - hostname: nostr.yourdomain.com service: ws://localhost:4869
- service: http_status:404 ```
- Note: In nano editor:
CTRL+Oand Enter to saveCTRL+Xto exit
-
Note: Check the credentials file path in the logs
-
Validate your configuration:
bash cloudflared tunnel validate -
Start the tunnel:
bash cloudflared tunnel run my-relay
Preventing Android from Killing the Tunnel
Run these commands to maintain tunnel stability:
bash date && apt install termux-tools && termux-setup-storage && termux-wake-lock echo "nameserver 1.1.1.1" > $PREFIX/etc/resolv.confTip: You can open multiple Termux sessions by swiping from the left edge of the screen while keeping your tunnel process running.
Updating Your Outbox Model Relays
Once your relay is running and accessible via your domain, you'll want to update your relay list in the Nostr network. This ensures other clients know about your relay and can connect to it.
Decoding npub (Public Key)
Private keys (nsec) and public keys (npub) are encoded in bech32 format, which includes: - A prefix (like nsec1, npub1 etc.) - The encoded data - A checksum
This format makes keys: - Easy to distinguish - Hard to copy incorrectly
However, most tools require these keys in hexadecimal (hex) format.
To decode an npub string to its hex format:
bash nak decode nostr:npub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4Change it with your own npub.
bash { "pubkey": "6e64b83c1f674fb00a5f19816c297b6414bf67f015894e04dd4c657e94102ee8" }Copy the pubkey value in quotes.
Create a kind 10002 event with your relay list:
- Include your new relay with write permissions
- Include other relays you want to read from and write to, omit 3rd parameter to make it both read and write
Example format:
json { "kind": 10002, "tags": [ ["r", "wss://your-relay-domain.com", "write"], ["r", "wss://eden.nostr.land/"], ["r", "wss://nos.lol/"], ["r", "wss://nostr.bitcoiner.social/"], ["r", "wss://nostr.mom/"], ["r", "wss://relay.primal.net/"], ["r", "wss://nostr.wine/", "read"], ["r", "wss://relay.damus.io/"], ["r", "wss://relay.nostr.band/"], ["r", "wss://relay.snort.social/"] ], "content": "" }Save it to a file called
event.jsonNote: Add or remove any relays you want. To check your existing 10002 relays: - Visit https://nostr.band/?q=by%3Anpub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4+++kind%3A10002 - nostr.band is an indexing service, it probably has your relay list. - Replace
npub1xxxin the URL with your own npub - Click "VIEW JSON" from the menu to see the raw event - Or use thenaktool if you know the relaysbash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.comReplace `<your-pubkey>` with your public key in hex format (you can get it using `nak decode <your-npub>`)- Sign and publish the event:
- Use a Nostr client that supports kind 10002 events
- Or use the
nakcommand-line tool:bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)
Important Security Notes: 1. Never share your nsec (private key) with anyone 2. Consider using NIP-49 encrypted keys for better security 3. Never paste your nsec or private key into the terminal. The command will be saved in your shell history, exposing your private key. To clear the command history: - For bash: use
history -c- For zsh: usefc -Wto write history to file, thenfc -pto read it back - Or manually edit your shell history file (e.g.,~/.zsh_historyor~/.bash_history) 4. if you're usingzsh, usefc -pto prevent the next command from being saved to history 5. Or temporarily disable history before running sensitive commands:bash unset HISTFILE nak key encrypt ... set HISTFILEHow to securely create NIP-49 encypted private key
```bash
Read your private key (input will be hidden)
read -s SECRET
Read your password (input will be hidden)
read -s PASSWORD
encrypt command
echo "$SECRET" | nak key encrypt "$PASSWORD"
copy and paste the ncryptsec1 text from the output
read -s ENCRYPTED nak key decrypt "$ENCRYPTED"
clear variables from memory
unset SECRET PASSWORD ENCRYPTED ```
On a Windows command line, to read from stdin and use the variables in
nakcommands, you can use a combination ofset /pto read input and then use those variables in your command. Here's an example:```bash @echo off set /p "SECRET=Enter your secret key: " set /p "PASSWORD=Enter your password: "
echo %SECRET%| nak key encrypt %PASSWORD%
:: Clear the sensitive variables set "SECRET=" set "PASSWORD=" ```
If your key starts with
ncryptsec1, thenaktool will securely prompt you for a password when using the--secparameter, unless the command is used with a pipe< >or|.bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)- Verify the event was published:
- Check if your relay list is visible on other relays
-
Use the
naktool to fetch your kind 10002 events:bash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.com -
Testing your relay:
- Try connecting to your relay using different Nostr clients
- Verify you can both read from and write to your relay
- Check if events are being properly stored and retrieved
- Tip: Use multiple Nostr clients to test different aspects of your relay
Note: If anyone in the community has a more efficient method of doing things like updating outbox relays, please share your insights in the comments. Your expertise would be greatly appreciated!
-
 @ e39333da:7c66e53a
2025-05-13 11:26:31
@ e39333da:7c66e53a
2025-05-13 11:26:31::youtube{#ELC4r7fbKEQ}
Silver Palace, developed by Silver Studio and published by Elementa, a fantasy adventure action RPG, built with Unreal Engine 5, was announced along with a 10-minute long gameplay video showcasing the game in what appears to be a pre-beta state.
::youtube{#EIUa74hDJiQ}
Find more information about the game from the game's website.
-
 @ 7e538978:a5987ab6
2025-05-13 10:59:37
@ 7e538978:a5987ab6
2025-05-13 10:59:37Introduction
Nostr Wallet Connect (NWC) is a powerful open protocol built on Nostr that enables a connection between Bitcoin Lightning wallets and applications—offering strong privacy, user control, easy connection, open interoperability, and support for a wide range of use cases without needing port forwarding or other network configuration. It allows a user to use many different Lightning apps with their own Lightning node via NWC.
In this post, we’ll give an overview of NWC as well as how to use a home-hosted LNbits instance as a private funding source for a public LNbits instance—giving you the benefits of privacy, control, and simplicity, to unleash the full power of LNbits.
Why Self-host with NWC?
- Privacy: Keep your Lightning node and LNbits instance at home, within your own network.
- Ownership & Control: Retain full custody of your funds, with no third-parties.
- Security: No port forwarding or VPN required—your node is not accessible from the public internet.
- Simplicity: Easy to set up and maintain.
- Flexible Funding: Fund your clearnet LNbits with any NWC-capable service—including your own LNbits instance, Alby, Minibits, Coinos, and more.
- App Access: Use LNbits at home as a Lightning wallet for one of the many NWC compatible apps.
How It Works
Your home Lightning node (running Raspiblitz, Umbrel, Start9, MyNode or one of the many other node packages) runs LNbits. You enable the NWCProvider extension in LNbits and generate a connection string.
On your clearnet LNbits instance (hosted with the LNbits SaaS or on your own VPS), set this connection string as your funding source.
This lets you:
- Fund and use LNbits from anywhere
- Keep your node private
- Add or change funding sources at any time with minimal config
How To Set It Up
1. Install LNbits at Home
Use a Raspiblitz, MyNode, Umbrel or other node package to run your home LNbits instance. You can also build your own node with Phoenixd and LNbits or any other combination of LNbits and Lightning node software.
-
Enable the
NWCProviderextension -
Create a new NWC connection

- Copy the NWC connection string

2. Provision a Clearnet LNbits Instance
Use:
- LNbits SaaS
- Your own VPS on a VPS provider like Vultr, Linode, AWC EC2 and install LNbits
3. Connect via NWC
On your clearnet LNbits instance:
-
Go to Settings → Funding
-
Select "Nostr Wallet Connect"
-
Paste your copied NWC connection string
-
Click Save, then Restart Server

Done! 🎉 Your clearnet LNbits instance is now funded by your home Lightning node—no open ports, no VPN, no fuss.
Home Nodes
You can use this setup with any LNbits-compatible home Lightning node, including:
- Raspiblitz
- Start9
- Umbrel
- MyNode
- Your own home server box with LNbits plus any other Lightning funding source for example Phoenixd, Core-Lightning, LND, etc.
Try it Out
Want to try this yourself?
- 🧠 Enjoy control, privacy, and simplicity
- 🌍 Use LNbits on the clearnet with funding from your own node
- 🔌 Connect apps like Alby, Minibits, Coinos, or your own LNbits
🚀 Run LNbits
Start exploring the power of NWC and LNbits today:
NWC Apps
Here are some great apps that make use of NWC.
- Alby Go
- A lightning wallet that uses one or many NWC providers to make and receive lightning payments
- Damus
- Decentralised social app on Nostr
- Amethyst
- Android Nostr social media client client
- Clean interface, popular among mobile users
- Snort
- Web-based Nostr client
- Familiar UI, easy access via browser
- Stacker News
- Bitcoin-centric news/discussion site
- Earn sats via upvotes
- Zeus
- Mobile app for controlling your own Lightning node
- Favoured by self-custody and privacy-focused users
Resources
-
 @ f32184ee:6d1c17bf
2025-04-23 13:21:52
@ f32184ee:6d1c17bf
2025-04-23 13:21:52Ads Fueling Freedom
Ross Ulbricht’s "Decentralize Social Media" painted a picture of a user-centric, decentralized future that transcended the limitations of platforms like the tech giants of today. Though focused on social media, his concept provided a blueprint for decentralized content systems writ large. The PROMO Protocol, designed by NextBlock while participating in Sovereign Engineering, embodies this blueprint in the realm of advertising, leveraging Nostr and Bitcoin’s Lightning Network to give individuals control, foster a multi-provider ecosystem, and ensure secure value exchange. In this way, Ulbricht’s 2021 vision can be seen as a prescient prediction of the PROMO Protocol’s structure. This is a testament to the enduring power of his ideas, now finding form in NextBlock’s innovative approach.
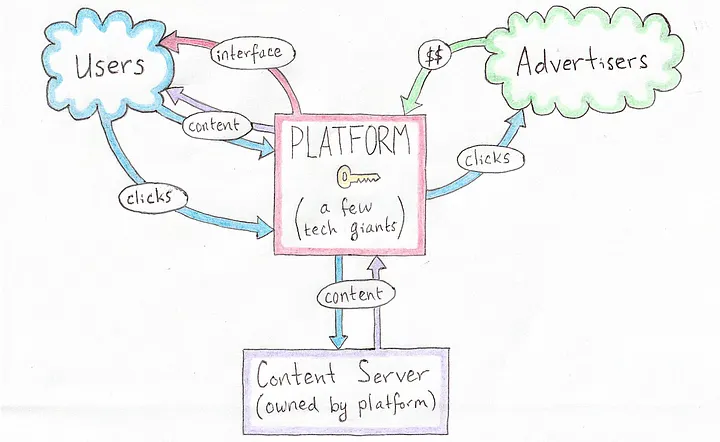 [Current Platform-Centric Paradigm, source: Ross Ulbricht's Decentralize Social Media]
[Current Platform-Centric Paradigm, source: Ross Ulbricht's Decentralize Social Media]Ulbricht’s Vision: A Decentralized Social Protocol
In his 2021 Medium article Ulbricht proposed a revolutionary vision for a decentralized social protocol (DSP) to address the inherent flaws of centralized social media platforms, such as privacy violations and inconsistent content moderation. Writing from prison, Ulbricht argued that decentralization could empower users by giving them control over their own content and the value they create, while replacing single, monolithic platforms with a competitive ecosystem of interface providers, content servers, and advertisers. Though his focus was on social media, Ulbricht’s ideas laid a conceptual foundation that strikingly predicts the structure of NextBlock’s PROMO Protocol, a decentralized advertising system built on the Nostr protocol.
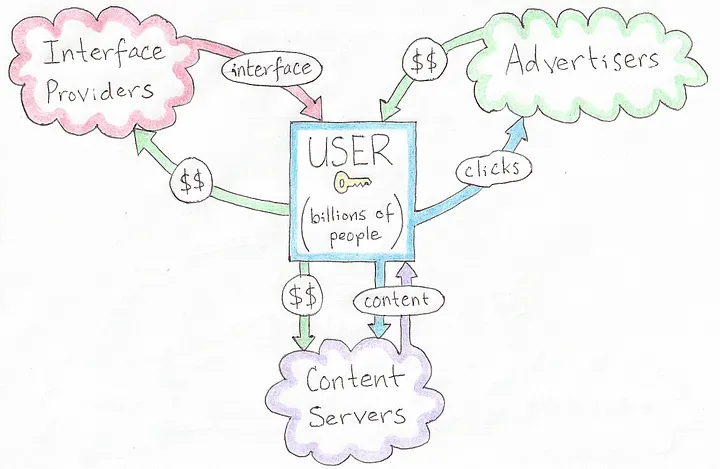 [A Decentralized Social Protocol (DSP), source: Ross Ulbricht's Decentralize Social Media]
[A Decentralized Social Protocol (DSP), source: Ross Ulbricht's Decentralize Social Media]Ulbricht’s Principles
Ulbricht’s article outlines several key principles for his DSP: * User Control: Users should own their content and dictate how their data and creations generate value, rather than being subject to the whims of centralized corporations. * Decentralized Infrastructure: Instead of a single platform, multiple interface providers, content hosts, and advertisers interoperate, fostering competition and resilience. * Privacy and Autonomy: Decentralized solutions for profile management, hosting, and interactions would protect user privacy and reduce reliance on unaccountable intermediaries. * Value Creation: Users, not platforms, should capture the economic benefits of their contributions, supported by decentralized mechanisms for transactions.
These ideas were forward-thinking in 2021, envisioning a shift away from the centralized giants dominating social media at the time. While Ulbricht didn’t specifically address advertising protocols, his framework for decentralization and user empowerment extends naturally to other domains, like NextBlock’s open-source offering: the PROMO Protocol.
NextBlock’s Implementation of PROMO Protocol
The PROMO Protocol powers NextBlock's Billboard app, a decentralized advertising protocol built on Nostr, a simple, open protocol for decentralized communication. The PROMO Protocol reimagines advertising by: * Empowering People: Individuals set their own ad prices (e.g., 500 sats/minute), giving them direct control over how their attention or space is monetized. * Marketplace Dynamics: Advertisers set budgets and maximum bids, competing within a decentralized system where a 20% service fee ensures operational sustainability. * Open-Source Flexibility: As an open-source protocol, it allows multiple developers to create interfaces or apps on top of it, avoiding the single-platform bottleneck Ulbricht critiqued. * Secure Payments: Using Strike Integration with Bitcoin Lightning Network, NextBlock enables bot-resistant and intermediary-free transactions, aligning value transfer with each person's control.
This structure decentralizes advertising in a way that mirrors Ulbricht’s broader vision for social systems, with aligned principles showing a specific use case: monetizing attention on Nostr.
Aligned Principles
Ulbricht’s 2021 article didn’t explicitly predict the PROMO Protocol, but its foundational concepts align remarkably well with NextBlock's implementation the protocol’s design: * Autonomy Over Value: Ulbricht argued that users should control their content and its economic benefits. In the PROMO Protocol, people dictate ad pricing, directly capturing the value of their participation. Whether it’s their time, influence, or digital space, rather than ceding it to a centralized ad network. * Ecosystem of Providers: Ulbricht envisioned multiple providers replacing a single platform. The PROMO Protocol’s open-source nature invites a similar diversity: anyone can build interfaces or tools on top of it, creating a competitive, decentralized advertising ecosystem rather than a walled garden. * Decentralized Transactions: Ulbricht’s DSP implied decentralized mechanisms for value exchange. NextBlock delivers this through the Bitcoin Lightning Network, ensuring that payments for ads are secure, instantaneous and final, a practical realization of Ulbricht’s call for user-controlled value flows. * Privacy and Control: While Ulbricht emphasized privacy in social interactions, the PROMO Protocol is public by default. Individuals are fully aware of all data that they generate since all Nostr messages are signed. All participants interact directly via Nostr.
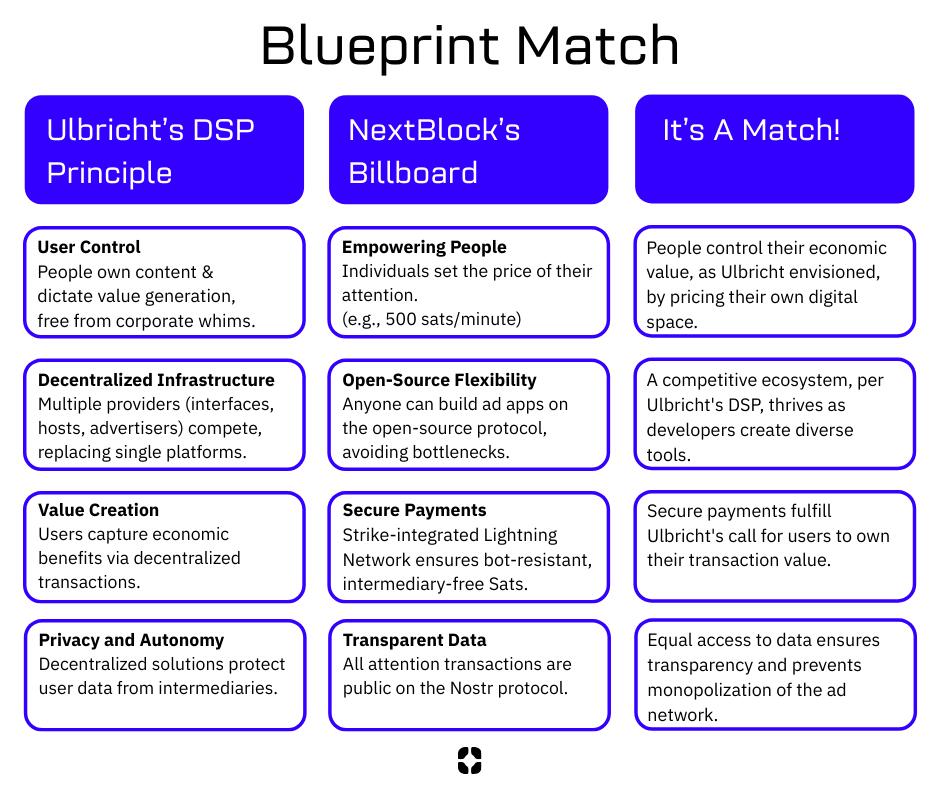 [Blueprint Match, source NextBlock]
[Blueprint Match, source NextBlock]
Who We Are
NextBlock is a US-based new media company reimagining digital ads for a decentralized future. Our founders, software and strategy experts, were hobbyist podcasters struggling to promote their work online without gaming the system. That sparked an idea: using new tech like Nostr and Bitcoin to build a decentralized attention market for people who value control and businesses seeking real connections.
Our first product, Billboard, is launching this June.
Open for All
Our model’s open-source! Check out the PROMO Protocol, built for promotion and attention trading. Anyone can join this decentralized ad network. Run your own billboard or use ours. This is a growing ecosystem for a new ad economy.
Our Vision
NextBlock wants to help build a new decentralized internet. Our revolutionary and transparent business model will bring honest revenue to companies hosting valuable digital spaces. Together, we will discover what our attention is really worth.
Read our Manifesto to learn more.
NextBlock is registered in Texas, USA.
-
 @ 57d1a264:69f1fee1
2025-05-13 11:33:23
@ 57d1a264:69f1fee1
2025-05-13 11:33:23This post is part of a series. It is meant to be a place for stackers to discuss creative projects they have been working on, or ideas they are aiming to build. Regardless of your project being personal, professional, physical, digital, or even simply an idea to brainstorm together.
If you have any creative projects or ideas that you have been working on or want to eventually work on... This is a place for discussing those, gather initial feedback and feel more energetic on bringing it to the next level.
Thank you @sangekrypto, @nkmg1c_ventures and @SilkyNinja for your contributions in the previous edition https://stacker.news/items/966136/r/DeSign_r Look forward to hearing if there's any progress there.
₿e Creative, have Fun! :D
originally posted at https://stacker.news/items/978934
-
 @ 9bde4214:06ca052b
2025-04-22 18:13:37
@ 9bde4214:06ca052b
2025-04-22 18:13:37"It's gonna be permissionless or hell."
Gigi and gzuuus are vibing towards dystopia.
Books & articles mentioned:
- AI 2027
- DVMs were a mistake
- Careless People by Sarah Wynn-Williams
- Takedown by Laila michelwait
- The Ultimate Resource by Julian L. Simon
- Harry Potter by J.K. Rowling
- Momo by Michael Ende
In this dialogue:
- Pablo's Roo Setup
- Tech Hype Cycles
- AI 2027
- Prompt injection and other attacks
- Goose and DVMCP
- Cursor vs Roo Code
- Staying in control thanks to Amber and signing delegation
- Is YOLO mode here to stay?
- What agents to trust?
- What MCP tools to trust?
- What code snippets to trust?
- Everyone will run into the issues of trust and micropayments
- Nostr solves Web of Trust & micropayments natively
- Minimalistic & open usually wins
- DVMCP exists thanks to Totem
- Relays as Tamagochis
- Agents aren't nostr experts, at least not right now
- Fix a mistake once & it's fixed forever
- Giving long-term memory to LLMs
- RAG Databases signed by domain experts
- Human-agent hybrids & Chess
- Nostr beating heart
- Pluggable context & experts
- "You never need an API key for anything"
- Sats and social signaling
- Difficulty-adjusted PoW as a rare-limiting mechanism
- Certificate authorities and centralization
- No solutions to policing speech!
- OAuth and how it centralized
- Login with nostr
- Closed vs open-source models
- Tiny models vs large models
- The minions protocol (Stanford paper)
- Generalist models vs specialized models
- Local compute & encrypted queries
- Blinded compute
- "In the eyes of the state, agents aren't people"
- Agents need identity and money; nostr provides both
- "It's gonna be permissionless or hell"
- We already have marketplaces for MCP stuff, code snippets, and other things
- Most great stuff came from marketplaces (browsers, games, etc)
- Zapstore shows that this is already working
- At scale, central control never works. There's plenty scams and viruses in the app stores.
- Using nostr to archive your user-generated content
- HAVEN, blossom, novia
- The switcharoo from advertisements to training data
- What is Truth?
- What is Real?
- "We're vibing into dystopia"
- Who should be the arbiter of Truth?
- First Amendment & why the Logos is sacred
- Silicon Valley AI bros arrogantly dismiss wisdom and philosophy
- Suicide rates & the meaning crisis
- Are LLMs symbiotic or parasitic?
- The Amish got it right
- Are we gonna make it?
- Careless People by Sarah Wynn-Williams
- Takedown by Laila michelwait
- Harry Potter dementors & Momo's time thieves
- Facebook & Google as non-human (superhuman) agents
- Zapping as a conscious action
- Privacy and the internet
- Plausible deniability thanks to generative models
- Google glasses, glassholes, and Meta's Ray Ben's
- People crave realness
- Bitcoin is the realest money we ever had
- Nostr allows for real and honest expression
- How do we find out what's real?
- Constraints, policing, and chilling effects
- Jesus' plans for DVMCP
- Hzrd's article on how DVMs are broken (DVMs were a mistake)
- Don't believe the hype
- DVMs pre-date MCP tools
- Data Vending Machines were supposed to be stupid: put coin in, get stuff out.
- Self-healing vibe-coding
- IP addresses as scarce assets
- Atomic swaps and the ASS protocol
- More marketplaces, less silos
- The intensity of #SovEng and the last 6 weeks
- If you can vibe-code everything, why build anything?
- Time, the ultimate resource
- What are the LLMs allowed to think?
- Natural language interfaces are inherently dialogical
- Sovereign Engineering is dialogical too
-
 @ a5ee4475:2ca75401
2025-05-13 11:31:33
@ a5ee4475:2ca75401
2025-05-13 11:31:33clients #list #descentralismo #english #article #finalversion
*These clients are generally applications on the Nostr network that allow you to use the same account, regardless of the app used, keeping your messages and profile intact.
**However, you may need to meet certain requirements regarding access and account NIP for some clients, so that you can access them securely and use their features correctly.
CLIENTS
Twitter like
- Nostrmo - [source] 🌐🤖🍎💻(🐧🪟🍎)
- Coracle - Super App [source] 🌐
- Amethyst - Super App with note edit, delete and other stuff with Tor [source] 🤖
- Primal - Social and wallet [source] 🌐🤖🍎
- Iris - [source] 🌐🤖🍎
- Current - [source] 🤖🍎
- FreeFrom 🤖🍎
- Openvibe - Nostr and others (new Plebstr) [source] 🤖🍎
- Snort 🌐(🤖[early access]) [onion] [source]
- Damus 🍎 [source]
- Nos 🍎 [source]
- Nostur 🍎 [source]
- NostrBand 🌐 [info] [source]
- Yana 🤖🍎🌐💻(🐧) [source]
- Nostribe [on development] 🌐 [source]
- Lume 💻(🐧🪟🍎) [info] [source]
- Gossip - [source] 💻(🐧🪟🍎)
- Camelus [early access] 🤖 [source]
Communities
- CCNS - Community Curated Nostr Stuff [source]
- noStrudel - Gamified Experience [onion] [info/source] 🌐
- [Nostrudel Next] - [onion]
- moStard - Nostrudel with Monero [onion] [info/source] 🌐
- Nostr Kiwi [creator] 🌐
- Satellite [info] 🌐
- Flotilla - [source] 🌐🐧
- Chachi - [source] 🌐
- Futr - Coded in haskell [source] 🐧 (others soon)
- Soapbox - Comunnity server [info] [source] 🌐
- Ditto - Soapbox comunnity server 🌐 [source] 🌐
- Cobrafuma - Nostr brazilian community on Ditto [info] 🌐
- Zapddit - Reddit like [source] 🌐
- Voyage (Reddit like) [on development] 🤖
Wiki
Search
- Advanced nostr search - Advanced note search by isolated terms related to a npub profile [source] 🌐
- Nos Today - Global note search by isolated terms [info] [source] 🌐
- Nostr Search Engine - API for Nostr clients [source]
- Ntrends - Trending notes and profiles 🌐
Website
App Store
ZapStore - Permitionless App Store [source] 🤖 💻(🐧🍎)
Video and Live Streaming
- Flare - Youtube like 🌐 [source]
- ZapStream - Live streaming and zap who you want (NIP-53) [source] 🤖(on zapstore) 🌐
- Swae - Live streaming [source] (on development) ⏳
Audio and Podcast Transmission
- Castr - Your npub as podcast feed [source]
- Nostr Nests - Audio Chats [source] 🌐
- Fountain - Podcast [source] 🤖🍎
- Corny Chat - Audio Chat [source] 🌐
Music
- Tidal - Music Streaming [source] [about] [info] 🤖🍎🌐
- Wavlake - Music Streaming [source] 🌐(🤖🍎 [early access])
- Tunestr - Musical Events [source] [about] 🌐
- Stemstr - Musical Colab (paid to post) [source] [about] 🌐
Images
- Lumina - Trending images and pictures [source] 🌐
- Pinstr - Pinterest like [source] 🌐
- Slidestr - DeviantArt like [source] 🌐
- Memestr - ifunny like [source] 🌐
Download and Upload
Documents, graphics and tables
- Mindstr - Mind maps [source] 🌐
- Docstr - Share Docs [info] [source] 🌐
- Formstr - Share Forms [info] 🌐
- Sheetstr - Share Spreadsheets [source] 🌐
- Slide Maker - Share slides 🌐 (advice: https://zaplinks.lol/ and https://zaplinks.lol/slides/ sites are down)
Health
- Sobrkey - Sobriety and mental health [source] 🌐
- NosFabrica - Finding ways for your health data 🌐
- LazerEyes - Eye prescription by DM [source] 🌐
Forum
- OddBean - Hacker News like [info] [source] 🌐
- LowEnt - Forum [info] 🌐
- Swarmstr - Q&A / FAQ [info] 🌐
- Staker News - Hacker News like 🌐 [info]
Direct Messenges (DM)
- 0xchat 🤖🍎 [source]
- Nostr Chat 🌐🍎 [source]
- Blowater 🌐 [source]
- Anigma (new nostrgram) - Telegram based [on development] [source]
- Keychat - Signal based [🤖🍎 on development] [source]
Reading
- nRSS - Nostr RSS reader 🌐
- Highlighter - Insights with a highlighted read [info] 🌐
- Zephyr - Calming to Read [info] 🌐
- Flycat - Clean and Healthy Feed [info] 🌐
- Nosta - Check Profiles [on development] [info] 🌐
- Alexandria - e-Reader and Nostr Knowledge Base (NKB) [source] 🌐
Writing
Lists
- Following - Users list [source] 🌐
- Nostr Unfollower - Nostr Unfollower
- Listr - Lists [source] 🌐
- Nostr potatoes - Movies List source 💻(numpy)
Market and Jobs
- Shopstr - Buy and Sell [source] 🌐
- Nostr Market - Buy and Sell 🌐
- Plebeian Market - Buy and Sell [source] 🌐
- Ostrich Work - Jobs [source] 🌐
- Nostrocket - Jobs [source] 🌐
Data Vending Machines - DVM (NIP90)
(Data-processing tools)
Games
- Chesstr - Chess 🌐 [source]
- Jestr - Chess [source] 🌐
- Snakestr - Snake game [source] 🌐
- DEG Mods - Decentralized Game Mods [info] [source] 🌐
- NG Engine - Nostr Game Engine [source] 🌐
- JmonkeyEngine - Java game engine [source] 🌐
Customization
Like other Services
- Olas - Instagram like [source] 🤖🍎🌐
- Nostree - Linktree like 🌐
- Rabbit - TweetDeck like [info] 🌐
- Zaplinks - Nostr links 🌐
- Omeglestr - Omegle-like Random Chats [source] 🌐
General Uses
- Njump - HTML text gateway source 🌐
- Filestr - HTML midia gateway [source] 🌐
- W3 - Nostr URL shortener [source] 🌐
- Playground - Test Nostr filters [source] 🌐
- Spring - Browser 🌐
Places
- Wherostr - Travel and show where you are
- Arc Map (Mapstr) - Bitcoin Map [info]
Driver and Delivery
- RoadRunner - Uber like [on development] ⏱️
- Nostrlivery - iFood like [on development] ⏱️
[⚠️SCAM⚠️] Arcade City - Uber like [source]
OTHER STUFF
Lightning Wallets (zap)
- Alby - Native and extension [info] 🌐
- ZBD - Gaming and Social [info] 🤖🍎
- Wallet of Satoshi [info] 🤖🍎
- Minibits - Cashu mobile wallet [info] 🤖
- Blink - Opensource custodial wallet (KYC over 1000 usd) [source] 🤖🍎
- LNbits - App and extesion [source] 🤖🍎💻
- Zeus - [info] [source] 🤖🍎
Exchange
Media Server (Upload Links)
audio, image and video
Connected with Nostr (NIP):
- Nostr Build - Free and paid Upload [info] [source] 🌐
- NostrMedia - Written in Go with Nip 96 / Blossom (free and paid) [info] [source]
- Nostr Check - [info] [source] 🌐
- NostPic - [info] [source] 🌐
- Sovbit - Free and paid upload [info] [source] 🌐
- Voidcat - Nip-96 and Blossom [source] 🌐
- Primal Media - [source] 🌐
Blossom - Your Media Safer
Primal Blossom 🌐 NostrBuild Blossom - Free upload (max 100MiB) and paid [info] [source] 🌐
Paid Upload Only
Satellite CDN - prepaid upload (max 5GB each) [info] [source] 🌐
Without Nostr NIP:
- Pomf - Upload larger videos (max 1GB) [source]
- Catbox - max 200 MB [source]
- x0 - max 512 MiB [source]
Donation and payments
- Zapper - Easy Zaps [source] 🌐
- Autozap [source] 🌐
- Zapmeacoffee 🌐
- Nostr Zap 💻(numpy)
- Creatr - Creators subscription 🌐
- Geyzer - Crowdfunding [info] [source] 🌐
- Heya! - Crowdfunding [source]
Security
- Secret Border - Generate offline keys 💻(java)
- Umbrel - Your private relay [source] 🌐
Key signing and Extension
- Nowser - Account access keys 📱(🤖🍎) 💻(🐧🍎🪟)
- Nos2x - Account access keys 🌐
- Nsec.app 🌐 [info]
- Lume - [info] [source] 🐧🪟🍎
- Satcom - Share files to discuss - [info] 🌐
- KeysBand - Multi-key signing [source] 🌐
Code
- Nostrify - Share Nostr Frameworks 🌐
- Git Workshop (github like) [experimental] 🌐
- Gitstr (github like) [on development] ⏱️
- Osty [on development] [info] 🌐
- Python Nostr - Python Library for Nostr
- Sybil - Creating, managing and test Nostr events [on development] ⏱️
Relay Check and Cloud
- Nostr Watch - See your relay speed 🌐
- NosDrive - Nostr Relay that saves to Google Drive
Bidges and Getways
- Matrixtr Bridge - Between Matrix & Nostr
- Mostr - Between Nostr & Fediverse
- Nostrss - RSS to Nostr
- Rsslay - Optimized RSS to Nostr [source]
- Atomstr - RSS/Atom to Nostr [source]
Useful Profiles and Trends
nostr-voice - Voice note (just some clients)
NOT RELATED TO NOSTR
Android Keyboards
Personal notes and texts
Front-ends
- Nitter - Twitter / X without your data [source]
- NewPipe - Youtube, Peertube and others, without account & your data [source] 🤖
- Piped - Youtube web without you data [source] 🌐
Other Services
- Brave - Browser [source]
- DuckDuckGo - Search [source]
- LLMA - Meta - Meta open source AI [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Proton Mail - Mail [source]
Other open source index: Degoogled Apps
Some other Nostr index on:
-
 @ 91bea5cd:1df4451c
2025-05-13 10:06:21
@ 91bea5cd:1df4451c
2025-05-13 10:06:21A Realidade por Trás dos Números
Padrão de Desagregação Familiar
- Países como Brasil (~55%) e Venezuela (~65%) apresentam não apenas altos índices de mães solo, mas também contextos de violência descontrolada.
- A desagregação da família nuclear tradicional não é causa única, mas é fator agravante quando associada à instabilidade cultural, abandono paterno e permissividade institucional.
- Homens ausentes e baixa exigência de responsabilidade paterna geram ciclos de pobreza, violência e ressentimento intergeracional.
Cultura da Irresponsabilidade
- Em muitos contextos, a paternidade é tratada como um ato opcional. A ausência de consequências legais, sociais e morais para o abandono paterno normaliza o ciclo de mães solteiras.
- Políticas públicas mal calibradas muitas vezes premiam o fracasso familiar com benefícios, sem exigir contrapartidas.
Inversão de Valores
- A valorização de comportamentos hedonistas, imediatistas e instáveis, promovidos culturalmente, mina qualquer tentativa de reconstrução familiar sólida.
- Em muitos casos, a maternidade é enfrentada sem planejamento ou estrutura mínima, gerando famílias instáveis e frágeis, mais propensas à violência e vulnerabilidade social.
Recomendações Realistas e Não Assistencialistas
Reforço da Responsabilidade Paterna
- Criar mecanismos legais mais rigorosos e efetivos de responsabilização civil e criminal para pais ausentes.
- Estimular socialmente o resgate do papel paterno, valorizando não apenas a presença física, mas o compromisso emocional e financeiro.
Incentivo à Formação Familiar Estável
- Reformar o currículo escolar para incluir educação sobre vínculos afetivos, responsabilidade conjugal e parentalidade realista.
- Desestimular a glamorização de estruturas familiares instáveis, combatendo a ideia de que qualquer forma familiar é igualmente funcional sob qualquer condição.
Cultura da Autossuficiência e Planejamento
- Substituir políticas puramente assistenciais por programas de incentivo ao planejamento familiar e responsabilidade pessoal, com foco na autonomia financeira e educacional antes da maternidade/paternidade.
- Campanhas públicas de conscientização sobre os impactos reais da desestrutura familiar na violência social e no desenvolvimento infantil.
O aumento da violência em países com alta proporção de mães solteiras não é uma coincidência, mas uma consequência de fatores culturais e sociais profundamente negligenciados.
Reverter esse cenário não exige mais Estado, mas sim mais responsabilidade individual, mais cobrança social e menos permissividade institucional. Qualquer solução duradoura passa por restaurar o valor da família como núcleo formador de caráter e estabilidade, não apenas como estatística para justificar políticas públicas.
-
 @ a39d19ec:3d88f61e
2025-04-22 12:44:42
@ a39d19ec:3d88f61e
2025-04-22 12:44:42Die Debatte um Migration, Grenzsicherung und Abschiebungen wird in Deutschland meist emotional geführt. Wer fordert, dass illegale Einwanderer abgeschoben werden, sieht sich nicht selten dem Vorwurf des Rassismus ausgesetzt. Doch dieser Vorwurf ist nicht nur sachlich unbegründet, sondern verkehrt die Realität ins Gegenteil: Tatsächlich sind es gerade diejenigen, die hinter jeder Forderung nach Rechtssicherheit eine rassistische Motivation vermuten, die selbst in erster Linie nach Hautfarbe, Herkunft oder Nationalität urteilen.
Das Recht steht über Emotionen
Deutschland ist ein Rechtsstaat. Das bedeutet, dass Regeln nicht nach Bauchgefühl oder politischer Stimmungslage ausgelegt werden können, sondern auf klaren gesetzlichen Grundlagen beruhen müssen. Einer dieser Grundsätze ist in Artikel 16a des Grundgesetzes verankert. Dort heißt es:
„Auf Absatz 1 [Asylrecht] kann sich nicht berufen, wer aus einem Mitgliedstaat der Europäischen Gemeinschaften oder aus einem anderen Drittstaat einreist, in dem die Anwendung des Abkommens über die Rechtsstellung der Flüchtlinge und der Europäischen Menschenrechtskonvention sichergestellt ist.“
Das bedeutet, dass jeder, der über sichere Drittstaaten nach Deutschland einreist, keinen Anspruch auf Asyl hat. Wer dennoch bleibt, hält sich illegal im Land auf und unterliegt den geltenden Regelungen zur Rückführung. Die Forderung nach Abschiebungen ist daher nichts anderes als die Forderung nach der Einhaltung von Recht und Gesetz.
Die Umkehrung des Rassismusbegriffs
Wer einerseits behauptet, dass das deutsche Asyl- und Aufenthaltsrecht strikt durchgesetzt werden soll, und andererseits nicht nach Herkunft oder Hautfarbe unterscheidet, handelt wertneutral. Diejenigen jedoch, die in einer solchen Forderung nach Rechtsstaatlichkeit einen rassistischen Unterton sehen, projizieren ihre eigenen Denkmuster auf andere: Sie unterstellen, dass die Debatte ausschließlich entlang ethnischer, rassistischer oder nationaler Kriterien geführt wird – und genau das ist eine rassistische Denkweise.
Jemand, der illegale Einwanderung kritisiert, tut dies nicht, weil ihn die Herkunft der Menschen interessiert, sondern weil er den Rechtsstaat respektiert. Hingegen erkennt jemand, der hinter dieser Kritik Rassismus wittert, offenbar in erster Linie die „Rasse“ oder Herkunft der betreffenden Personen und reduziert sie darauf.
Finanzielle Belastung statt ideologischer Debatte
Neben der rechtlichen gibt es auch eine ökonomische Komponente. Der deutsche Wohlfahrtsstaat basiert auf einem Solidarprinzip: Die Bürger zahlen in das System ein, um sich gegenseitig in schwierigen Zeiten zu unterstützen. Dieser Wohlstand wurde über Generationen hinweg von denjenigen erarbeitet, die hier seit langem leben. Die Priorität liegt daher darauf, die vorhandenen Mittel zuerst unter denjenigen zu verteilen, die durch Steuern, Sozialabgaben und Arbeit zum Erhalt dieses Systems beitragen – nicht unter denen, die sich durch illegale Einreise und fehlende wirtschaftliche Eigenleistung in das System begeben.
Das ist keine ideologische Frage, sondern eine rein wirtschaftliche Abwägung. Ein Sozialsystem kann nur dann nachhaltig funktionieren, wenn es nicht unbegrenzt belastet wird. Würde Deutschland keine klaren Regeln zur Einwanderung und Abschiebung haben, würde dies unweigerlich zur Überlastung des Sozialstaates führen – mit negativen Konsequenzen für alle.
Sozialpatriotismus
Ein weiterer wichtiger Aspekt ist der Schutz der Arbeitsleistung jener Generationen, die Deutschland nach dem Zweiten Weltkrieg mühsam wieder aufgebaut haben. Während oft betont wird, dass die Deutschen moralisch kein Erbe aus der Zeit vor 1945 beanspruchen dürfen – außer der Verantwortung für den Holocaust –, ist es umso bedeutsamer, das neue Erbe nach 1945 zu respektieren, das auf Fleiß, Disziplin und harter Arbeit beruht. Der Wiederaufbau war eine kollektive Leistung deutscher Menschen, deren Früchte nicht bedenkenlos verteilt werden dürfen, sondern vorrangig denjenigen zugutekommen sollten, die dieses Fundament mitgeschaffen oder es über Generationen mitgetragen haben.
Rechtstaatlichkeit ist nicht verhandelbar
Wer sich für eine konsequente Abschiebepraxis ausspricht, tut dies nicht aus rassistischen Motiven, sondern aus Respekt vor der Rechtsstaatlichkeit und den wirtschaftlichen Grundlagen des Landes. Der Vorwurf des Rassismus in diesem Kontext ist daher nicht nur falsch, sondern entlarvt eine selektive Wahrnehmung nach rassistischen Merkmalen bei denjenigen, die ihn erheben.
-
 @ 866e0139:6a9334e5
2025-05-13 09:47:28
@ 866e0139:6a9334e5
2025-05-13 09:47:28Autor: Lilly Gebert. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Wie fühlst Du dich, nachdem Du mit deinem Partner oder deiner Partnerin, oder sonst einem Menschen geschlafen hast – nachdem der Drang und die Erregung ein Ende gefunden haben? Gut – oder schlecht? Befriedigt – oder unbefriedigt? Verbunden – oder getrennt? Erfüllt – oder leer? Was geht dir durch den Kopf? Warum überhaupt geht dir irgendetwas durch den Kopf? Warum bleibst Du dich nicht in deinem Körper – in seiner noch anhaltenden Nähe zu dem Körper, mit dem Du gerade noch eins warst? Vielleicht weil Du dich davon ablenken möchtest, dass ihr gerade dies nicht wart? Dass ihr nicht «eins» wart; sondern zwei, die für einen Moment Druck abgelassen haben – ohne höheren Sinn und ohne tieferes Gefühl? Ist das der Grund, weswegen Du lieber in die Verklärungen deines Verstandes abdriftest, anstatt die gerade erlebte Verbindung noch etwas in deinem Körper nachklingen zu lassen? Ist das allgemein der Grund, weswegen Du lieber in Rationalitäten lebst? Um dir nicht eingestehen zu müssen, wie unverbunden Du wirklich bist? Wie unverbunden und allein, ohne tiefere Verbindung zu dir oder einem anderen Menschen? Ist es das? Ist es das, was Du einfach nicht wahrhaben kannst? Und weswegen Du lieber die Masse an Oberflächlichkeit suchst, um bloß nie in einer Beziehung zu enden, in der Du an deine eigene Unfähigkeit erinnert wirst, gerade dies zu sein – in Beziehung?
***
Vielleicht beginnt alle Trennung dieser Welt mit der Verwechslung von Sex und Nähe, Nähe und Liebe, als auch Liebe und Frieden. Du sehnst dich nach dem einen und jagst doch dem anderen hinterher. Wie kann das sein?
Liegt es daran, dass Du als Kind keine stabilen Beziehungen erfahren hast und diese aus dem Grund auch im Erwachsenenalter nicht leben kannst? Hast Du einst schlechte Erfahrungen mit Intimität und Nähe gemacht, aufgrund derer etwas in dir diese fortwährend verhindert, um dich zu «schützen»? Hältst Du dich selbst für nicht liebenswert und kannst deshalb auch im Außen keine Liebe annehmen? Oder hast Du Angst davor, durch die Nähe und Berührung eines anderen Menschen von etwas in dir selbst berührt zu werden, an dessen Existenz Du nicht erinnert werden möchtest?
Falls ja, warum gehst Du dann fortwährend «Beziehungen» zu anderen Menschen ein, bevor Du nicht die Beziehung zu dir selbst geklärt hast? Hast Du wirklich so sehr verlernt zu lieben und so weit vergessen, was Liebe ist, dass Du dich damit zufriedengibst? Ich glaube kaum. Und ich glaube, Du spürst das auch. Ganz tief in dir sehnt auch deine Seele sich nach einer Begegnung, in der Du nichts von dir zurückhalten musst. In der Du ganz, und damit ganz Du sein kannst.
Doch was machst Du stattdessen? Du unterdrückst diese Sehnsucht, verneinst deinen innersten Herzenswunsch nach Berührung, nach Nähe, nach Liebe. Und damit auch jedes Bedürfnis, was mit seinem ausbleibenden Ausdruck ebenfalls unterdrückt wird. Langsam, ganz langsam hörst Du auf, über deine Gefühle zu sprechen, Du hörst auf, deine Grenzen zu wahren, das zu machen, was dich dir selbst näherbringt. Auf diese Weise machst Du dich selbst nicht nur immer kleiner, Du entfernst dich auch zusehends von deiner eigenen Lebendigkeit – dem eigentlichen Schlüssel zu jeder Beziehung, die nicht von Besitz und Lustbefriedigung, sondern von Selbstsein und Nähe getragen wird.
Falsche Versprechen: Verbindung statt Symbiose
Erich Fromm war es, der mit seinem 1956 erschienenen und insgesamt über 25 Millionen Mal verkauften Werk «Die Kunst des Liebens» erstmals herausgearbeitet hat, wie zerstörerisch unsere moderne Konsumgesellschaft doch für die Art und Weise ist, wie wir Beziehungen eingehen. Nicht nur die untereinander und zu uns selbst, sondern auch die zu Tier und Natur. Liebe, so schreibt Fromm, ist allem voran eine Haltung des Seins, nicht des Habens. Es gehe nicht darum, den anderen zu besitzen oder von ihm in Besitz genommen zu werden. Nicht Verschmelzung sei das Ziel, sondern das Selbstsein mit, oder auch trotz, der anderen Person.
Ohne dieses Selbstsein, das durch den modernen Glauben, alles sei käuflich, insofern untergraben wurde, dass nun auch der Mensch und seine Beziehungen als Objekte betrachtet würden, gäbe es laut Fromm keine Nähe – und ohne Nähe keinen wahren Frieden. «Sexualität», so schreibt er, könne «ein Mittel sein, um die Isolation zu überwinden – aber sie kann auch ein Ersatz für Liebe sein.» Womit ich hinzufügen würde: Wie Sexualität ein Ersatz für Liebe sein kann, so werden heute Konsum, Sicherheit und Ablenkung zum Ersatz für wahren Frieden. Und gleich wie Nähe zur Illusion von Intimität werden kann, werden falsche Sicherheitsversprechen oft zur Maskerade des Friedens – einer Stille, die nichts heilt.
Das ist der Zustand unserer Zeit: Sexualität ersetzt Liebe, Waffen ersetzen Frieden. Doch genauso wie Sex in Wahrheit keine Liebe ersetzt, ersetzt auch ein Wettrüsten keinen Frieden. Beides täuscht Nähe und Sicherheit vor, wo eigentlich Distanz und Kälte herrschen. Von ihnen eingenommen, hältst Du die Liebe, die dein Körper imitiert, für echt, und die äußere Ordnung, die dir simuliert wird, für den Frieden, von dem Du glauben, Du würdest ihn in dir tragen. Dabei bleibt beides leer, wenn dein Herz nicht mitgeht. Da ist weder Ordnung im Außen, noch Frieden in deinem Innern. Was herrscht, ist Krieg. Innen wie außen.

Wut im Innern, Krieg im Außen
Wer Nähe meidet, verlernt Frieden. Denn Frieden beginnt dort, wo Du aushältst, was ist. Nicht im Politischen, sondern in deiner eigenen Gerichtskammer: dem Austarieren und Verhandeln der eigenen Gefühle und Bedürfnisse – dem Eingeständnis, dass am Ende nicht der Sex das Problem ist, sondern dein Umgang mit Nähe; deine Unfähigkeit, mit dir selbst in Frieden zu sein – und dies darum auch mit dem Rest der Welt nicht bist. Nenn’ es Karma, das Gesetz der Anziehung oder eine traumatische Rückkopplungsschleife; aber wo immer Du diesen Blick nicht vom Außen zurück auf das Minenfeld in dir wendest, wird sich sein Krieg solange fortsetzen, bis Du der Wut, die mit ihm in dir hochkocht, Dampf verschaffst. Ob auf konstruktive oder destruktive Weise hängt davon ab, wie früh Du sie als das erkennst, woraus sie sich speist: deine unterdrückten Gefühle.
«Das grundsätzliche Ausweichen vor dem Wesentlichen ist das Problem des Menschen.» – Wilhelm Reich
In dieser Hinsicht noch radikaler als Fromm ging Wilhelm Reich vor. Als Schüler Sigmund Freuds sah er sexuelle Unterdrückung als Wurzel aller gesellschaftlichen Gewalt. Nur wer sexuell befreit sei – im Sinne von energetisch gelöst und beziehungsfähig – könne inneren Frieden erfahren. Ginge es nach Reich, so hängt gesellschaftlicher Frieden unmittelbar davon ab, wie weit es uns gelingt, uns körperlich zu entpanzern und emotional zu öffnen. Womit sein Ansatz in der Idee gipfelte, dass die gesellschaftliche Ordnung nicht durch äußere Gesetze, sondern durch die innere Struktur des Einzelnen geprägt wird. Diametral zu Marx, demzufolge es nicht das Bewusstsein der Menschen sei, das ihr Sein bestimmt, sondern umgekehrt ihr gesellschaftliches Sein, das ihr Bewusstsein bestimmt, beschrieb Reich also, wie emotionale Blockaden im Körper verankert seien und sich dort als chronische Spannungen manifestierten. Diese Panzerungen würden nicht nur freie Gefühlsäußerung verhindern, sondern stauten auch lebendige Energie an, was zu Aggression, Entfremdung und letztlich zu kollektiver Gewalt führen könne. Frieden, so Reich, beginne nicht in politischen Institutionen, sondern in der Fähigkeit des Einzelnen, Angst und Abwehr abzubauen, sich selbst zu spüren – und andere nicht als Bedrohung, sondern als lebendige Gegenüber wahrzunehmen.
Warum wir dies scheinbar nicht mehr können, warum aber kein Weg daran vorbeiführt, über den Frieden in uns heilsame Beziehungen einzugehen, wollen wir den Frieden auch außerhalb von uns – in der Welt, folgt im zweiten Teil dieses Texts.
Lilly Gebert betreibt den Substack-Blog "Treffpunkt im Unendlichen" und schreibt regelmäßig für "die Freien" und Manova. Zuletzt erschien von ihr "Das Gewicht der Welt". Im Herbst erscheint "Sein statt Haben. Enzyklopädie für eine neue Zeit." (vorbestellbar).
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:13:56
@ 4ba8e86d:89d32de4
2025-04-21 02:13:56Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ cefb08d1:f419beff
2025-05-13 10:49:43
@ cefb08d1:f419beff
2025-05-13 10:49:43What is the diference between a sea lion and a seal:
originally posted at https://stacker.news/items/978903
-
 @ 866e0139:6a9334e5
2025-05-13 09:36:08
@ 866e0139:6a9334e5
2025-05-13 09:36:08Autor: René Boyke. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Recht gilt als Fundament für Frieden. So predigen es die Lehrer in der Schule und die Professoren an den Universitäten. Mit der – theoretischen – Funktionsweise von Gerichten und deren Streitschlichtungsfunktion wird die Notwendigkeit und Verträglichkeit eines staatlichen Gewaltmonopols hergeleitet. Die Behauptung: Ohne staatliches Recht herrsche Chaos, das Recht des Stärkeren. Das Gedankenspiel des fiktiven Naturzustands, mit dem Hobbes bereits seinen übergriffigen Leviathan rechtfertigen konnte, überzeugt die meisten.
Mit Recht?
Larken Roses Kritik am Gewaltmonopol
Der libertäre Denker Larken Rose („The Most Dangerous Superstition“, deutscher Titel: „Die gefährlichste aller Religionen“, 2018) hält dagegen. Er argumentiert, staatliches Recht sei Ausdruck von Autorität und Zwang und institutionalisiere damit Gewalt. Und in der Tat: Der Staat nimmt für sich kein Friedensmonopol in Anspruch, sondern ein Gewaltmonopol.
Rose verdeutlicht, dass staatliches Recht auf Zwang basiert: Gesetze und Verordnungen können als Drohungen interpretiert werden, die mit Sanktionen, Strafen, Gefängnis oder mancherorts mit Todesstrafe durchgesetzt werden. Für Rose ist der Staat eine Gruppe von Räubern, denen durch den tief verwurzelten Glauben an Autoritäten ein legitimer Anstrich verpasst wird. Diese „Bande“ schaffe ständig Konflikte, etwa durch inszenierte Gefahren, aber auch durch Gesetze. So seien Steuergesetze seiner Meinung nach „legitimierter Raub“, die Widerstand provozieren und damit Unfrieden. Politiker würden sich nach Belieben eigene Regeln schaffen und selbst bestimmen, was gut und was schlecht sei.
Steigt Ihnen angesichts solcher Behauptungen bereits die Röte der Empörung ins Gesicht?
Doch können Sie ihm widersprechen? Können Sie leugnen, dass staatliche Gewalt von Politikern, Apparatschiks und Staatslenkern zum eignen Vorteil eingesetzt wird? Und müssen nicht auch Sie eingestehen, dass daraus Konflikte und Unfrieden entstehen? Hat Rose also Recht?
Rechtsstaatliche Defizite in Deutschland
Um solchen Missbrauch des Gewaltmonopols zu verhindern, gibt es die Gewaltenteilung: die Aufteilung staatlicher Macht in Legislative, Exekutive und Judikative sind Grundpfeiler der Demokratie, in Deutschland verankert im Grundgesetz. Damit diese Gewaltenteilung funktioniert, setzt sie unabhängige Institutionen voraus, insbesondere eine Trennung von der Politik. Haben wir diese in Deutschland?
Unsere Legislative leidet unter Koalitionsdisziplin und Fraktionszwang. Abgeordnete stimmen zu oft nach Parteilinie, nicht nach individuellem Gewissen. Unsere Judikative ist stark politisiert. So werden die Richter des Bundesverfassungsgerichts von einem Wahlausschuss gewählt, der aus Bundestags- und Bundesratsmitgliedern besteht, was eine Einladung für parteipolitische Deals ist – ganz zu schweigen davon, dass die Richter den Parteien oft eng verbunden sind bzw. oft selbst Politiker waren (siehe beispielhaft: Stephan Harbarth, Peter Müller, Christine Hohmann-Dennhardt) und von den regelmäßigen gemeinsamen Edeldiners zwischen Spitzen der Exekutive und der Judikative, die Sie und ich als Bürger zwar bezahlen aber nicht daran teilnehmen dürfen, ausgeschlossen werden, ganz zu schweigen. Besonders kritisch: Unsere Strafverfolgungsbehörden können durch die Weisungsgebundenheit der Staatsanwaltschaften politisch gesteuert werden. Dass der Verfolgungsdruck auf Regierungskritiker immer härter wird, ist mittlerweile offenkundig. Der Deutsche Richterbund forderte erst vor wenigen Tagen einen besseren Schutz der Justiz vor autoritären Kräften. Und auch bei der Exekutive sind die Mängel offensichtlich: So sollen die Behörden eigentlich die Gesetze ausführen, aber diese Anwendung ist allzu oft selektiv und interessengeleitet. Sich daran zu gewöhnen, dass ehemalige Regierungsmitglieder in Führungspositionen von Unternehmen wechseln und damit Interessenkonflikte heraufbeschwören, ist ebenfalls ein Zeichen eines kranken Rechtsstaats.
Und wie sieht es international aus?
Internationale rechtsstaatliche Defizite
In meinem letzten hier veröffentlichten Beitrag beleuchtete ich den Papiertiger des praktisch in Stein gemeißelten völkerrechtlichen Gewaltverbots. Man beruft sich darauf, wenn es einem nützt, und ansonsten ignoriert man es oder bemüht umständliche Ausflüchte, warum es nicht greife. Ähnliches lässt sich beim Internationalen Strafgerichtshof beobachten: Die Staaten, die die heißesten Kandidaten für Kriegsverbrechen sind, werden gar nicht erst Mitglied, und die übrigen folgen seinen Regeln nur, wenn es opportun ist. So hat der IStGH zwar einen Haftbefehl gegen Benjamin Netanjahu erlassen, aber er kann unbeirrt nach Ungarn reisen, obwohl dieses hätte vollstrecken müssen. Es darf meiner Meinung nach aber auch stark bezweifelt werden, ob Deutschland einen Haftbefehl gegen Netanjahu vollstrecken würde. Ein weiteres Beispiel völkerrechtswidrigen Handelns: Die Sanktionen gegen Russland.
Ganz unempört müssen wir leider feststellen: Unsere Schutzmechanismen, den Gewaltmissbrauch zu verhindern, sind mittlerweile arg durchlöchert und angeschlagen. Kann Larken Rose helfen?
Kann Larken Rose helfen?
Rose sieht Steuern als „legitimierten Raub“. In der Tat werden auch in Deutschland etwa die Abgaben für den öffentlich-rechtlichen Rundfunk falls nötig mittels Gerichtsvollziehern und Haft erzwungen. Ohne Frage handelt es sich dabei um Gewaltausübung, die konfliktträchtig ist. Doch der Staat legitimiert seine Gewaltausübung selbst. Polizeieinsätze gegen Kritiker der Corona-Maßnahmenpolitik erfolgten z.B. mittels grober Gewalt, nämlich Wasserwerfern und Pfefferspray gegen die Demonstranten. Auch der Europäische Gerichtshof für Menschenrechte verurteilte Deutschland bereits mehrfach wegen übermäßiger Polizeigewalt. Das sind Beispiele für Roses Vorbringen, dass der Staat Gewalt institutionalisiert, um Gehorsam zu erzwingen – und das erzeugt und verschärft Spannungen und Konflikte.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
\ Rose betont, dass staatliches Recht immer auf Zwang basiert. In Deutschland führt die Nichtbeachtung von Gesetzen – etwa bei Verkehrsdelikten – zu Bußgeldern, Führerscheinentzug oder Haft. Im Völkerrecht erzwingen Sanktionen, wie die gegen Russland, wirtschaftlichen Druck, der für Rose ebenfalls Gewalt ist. Diese Mechanismen bestätigen seine Sicht, dass der Staat Gewalt als Standardwerkzeug nutzt.
Vielleicht hat Ihre eventuell aufgetretene Empörungsröte die Blässe einsichtiger Scham angenommen. Wenn ja, ist das nicht ganz unbegründet. Rose hat völlig Recht damit, dass die buchstäblich gewaltigen Möglichkeiten des Staates gefährlich sein können. Und er hat recht damit, dass blindes Vertrauen darauf, dass Autoritäten mit dieser Gewalt schon maß- und verantwortungsvoll umgehen werden, völlig fehl am Platze ist.
Und auch eine andere zentrale Frage ist gerechtfertigt: Wenn der Staat die Legitimation seiner Macht daraus bezieht, dass die Bürger ihm diese Macht übertragen, wie kann es dann sein, dass der Staat Macht ausübt, die ein einzelner Bürger weder jemals innehat noch innehatte? Ein Paradoxon.
Selbstverantwortung als Heilmittel für den Rechtsstaat
Rose setzt daher statt eines Staates auf Freiwilligkeit und Selbsteigentum. Er betont, dass „Menschlichkeit Freiwilligkeit bedeutet“. Jede Interaktion sollte auf gegenseitigem Einverständnis beruhen, ohne Zwang durch Gesetze oder staatliche Institutionen. Einen Impfzwang schlösse dies also aus. Aber auch einen Tötungszwang in Form eines Kriegsdienstes, bei uns verbal zum „Wehrdienst“ aufgehübscht. Jeder Mensch habe das Recht, über sein Leben, seinen Körper und sein Eigentum zu bestimmen, ohne dass eine „Autorität“ eingreift.
Das klingt gut, aber müsste dieses „Selbsteigentum“ nicht auch wieder durch ein irgendwie geartetes Rechtssystem abgesichert werden? Und besteht nicht die Gefahr, dass statt der Polizei dann ein privates Sicherheitsunternehmen ein neues Gewaltmonopol erschafft? Offensichtlich ist eine völlig widerspruchsfreie Antwort auf das rechtsstaatliche Dilemma nicht so leicht zu finden.
Rose fordert zudem, dass Menschen unmoralische Gesetze ignorieren und aktiv Widerstand leisten, von passivem Ungehorsam bis hin zu gewaltsamen Aktionen, je nach Unterdrückungsgrad. Er sieht dies als Mittel, um die Illusion der staatlichen „Autorität“ zu brechen und Gewalt zu reduzieren.
Bei einigen mag hier bereits wieder die Empörungsröte emporsteigen, aber vielleicht hilft dagegen die Vergegenwärtigung folgender Fragen: War der Widerstand eines Mahatma Gandhi dem Recht eher dienlich oder eher schädlich? Und war der mutige, aber rechtswidrige Ungehorsam Rosa Parks’ eher wünschenswert als nicht? Hat ihr Widerstand zu mehr oder weniger Freiheit beigetragen? Haben uns die rechtswidrigen Offenlegungen Edward Snowdens und Julian Assanges nicht die Augen geöffnet, welche Verbrechen durch demokratische Staaten begangen werden?
Und ist die von Larken Rose eingeforderte Selbstverantwortung und sein Aufruf, dem eigenen Gewissen zu folgen, anstatt „Autorität“ zu gehorchen, nicht genau das Antiserum gegen einen übergriffigen, ja diktatorischen Staat, wie etwa unter der Naziherrschaft?
Selbt als Jurist wird man Rose in vielen Punkten zustimmen müssen und einsehen, dass es in vielen Fällen der Glaube an die Autorität ist, der erst das monströse Unrecht ermöglicht, dessen Zeugen wir sind.
Ich selbst halte es für sehr zweifelhaft, ob man wie Rose daraus die Abschaffung des Staates herleiten kann oder muss.
Nicht zweifelhaft ist hingegen, dass wir eine Stärkung individueller Selbstverantwortung brauchen. Kein Warten auf einen Erlöser, auf eine Partei. Aus dieser Selbstverantwortung heraus folgt die Ausbesserung der gezeigten – auch bei uns vorhandenen – rechtsstaatlichen Defizite.
Recht ohne individuelle Selbstverantwortung führt unweigerlich zu den genannten rechtsstaatlichen Konflikten und damit zu Unfrieden und Gewalt. Recht mit Selbstverantwortung kann hingegen zu einem friedlichen Rechtssystem führen.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ ed5774ac:45611c5c
2025-04-19 20:29:31
@ ed5774ac:45611c5c
2025-04-19 20:29:31April 20, 2020: The day I saw my so-called friends expose themselves as gutless, brain-dead sheep.
On that day, I shared a video exposing the damning history of the Bill & Melinda Gates Foundation's vaccine campaigns in Africa and the developing world. As Gates was on every TV screen, shilling COVID jabs that didn’t even exist, I called out his blatant financial conflict of interest and pointed out the obvious in my facebook post: "Finally someone is able to explain why Bill Gates runs from TV to TV to promote vaccination. Not surprisingly, it's all about money again…" - referencing his substantial investments in vaccine technology, including BioNTech's mRNA platform that would later produce the COVID vaccines and generate massive profits for his so-called philanthropic foundation.
The conflict of interest was undeniable. I genuinely believed anyone capable of basic critical thinking would at least pause to consider these glaring financial motives. But what followed was a masterclass in human stupidity.
My facebook post from 20 April 2020:

Not only was I branded a 'conspiracy theorist' for daring to question the billionaire who stood to make a fortune off the very vaccines he was shilling, but the brain-dead, logic-free bullshit vomited by the people around me was beyond pathetic. These barely literate morons couldn’t spell "Pfizer" without auto-correct, yet they mindlessly swallowed and repeated every lie the media and government force-fed them, branding anything that cracked their fragile reality as "conspiracy theory." Big Pharma’s rap sheet—fraud, deadly cover-ups, billions in fines—could fill libraries, yet these obedient sheep didn’t bother to open a single book or read a single study before screaming their ignorance, desperate to virtue-signal their obedience. Then, like spineless lab rats, they lined up for an experimental jab rushed to the market in months, too dumb to care that proper vaccine development takes a decade.
The pathetic part is that these idiots spend hours obsessing over reviews for their useless purchases like shoes or socks, but won’t spare 60 seconds to research the experimental cocktail being injected into their veins—or even glance at the FDA’s own damning safety reports. Those same obedient sheep would read every Yelp review for a fucking coffee shop but won't spend five minutes looking up Pfizer's criminal fraud settlements. They would demand absolute obedience to ‘The Science™’—while being unable to define mRNA, explain lipid nanoparticles, or justify why trials were still running as they queued up like cattle for their jab. If they had two brain cells to rub together or spent 30 minutes actually researching, they'd know, but no—they'd rather suck down the narrative like good little slaves, too dumb to question, too weak to think.
Worst of all, they became the system’s attack dogs—not just swallowing the poison, but forcing it down others’ throats. This wasn’t ignorance. It was betrayal. They mutated into medical brownshirts, destroying lives to virtue-signal their obedience—even as their own children’s hearts swelled with inflammation.
One conversation still haunts me to this day—a masterclass in wealth-worship delusion. A close friend, as a response to my facebook post, insisted that Gates’ assumed reading list magically awards him vaccine expertise, while dismissing his billion-dollar investments in the same products as ‘no conflict of interest.’ Worse, he argued that Gates’s $5–10 billion pandemic windfall was ‘deserved.’
This exchange crystallizes civilization’s intellectual surrender: reason discarded with religious fervor, replaced by blind faith in corporate propaganda.
The comment of a friend on my facebook post that still haunts me to this day:

Walking Away from the Herd
After a period of anger and disillusionment, I made a decision: I would no longer waste energy arguing with people who refused to think for themselves. If my circle couldn’t even ask basic questions—like why an untested medical intervention was being pushed with unprecedented urgency—then I needed a new community.
Fortunately, I already knew where to look. For three years, I had been involved in Bitcoin, a space where skepticism wasn’t just tolerated—it was demanded. Here, I’d met some of the most principled and independent thinkers I’d ever encountered. These were people who understood the corrupting influence of centralized power—whether in money, media, or politics—and who valued sovereignty, skepticism, and integrity. Instead of blind trust, bitcoiners practiced relentless verification. And instead of empty rhetoric, they lived by a simple creed: Don’t trust. Verify.
It wasn’t just a philosophy. It was a lifeline. So I chose my side and I walked away from the herd.
Finding My Tribe
Over the next four years, I immersed myself in Bitcoin conferences, meetups, and spaces where ideas were tested, not parroted. Here, I encountered extraordinary people: not only did they share my skepticism toward broken systems, but they challenged me to sharpen it.
No longer adrift in a sea of mindless conformity, I’d found a crew of thinkers who cut through the noise. They saw clearly what most ignored—that at the core of society’s collapse lay broken money, the silent tax on time, freedom, and truth itself. But unlike the complainers I’d left behind, these people built. They coded. They wrote. They risked careers and reputations to expose the rot. Some faced censorship; others, mockery. All understood the stakes.
These weren’t keyboard philosophers. They were modern-day Cassandras, warning of inflation’s theft, the Fed’s lies, and the coming dollar collapse—not for clout, but because they refused to kneel to a dying regime. And in their defiance, I found something rare: a tribe that didn’t just believe in a freer future. They were engineering it.
April 20, 2024: No more herd. No more lies. Only proof-of-work.
On April 20, 2024, exactly four years after my last Facebook post, the one that severed my ties to the herd for good—I stood in front of Warsaw’s iconic Palace of Culture and Science, surrounded by 400 bitcoiners who felt like family. We were there to celebrate Bitcoin’s fourth halving, but it was more than a protocol milestone. It was a reunion of sovereign individuals. Some faces I’d known since the early days; others, I’d met only hours before. We bonded instantly—heated debates, roaring laughter, zero filters on truths or on so called conspiracy theories.
As the countdown to the halving began, it hit me: This was the antithesis of the hollow world I’d left behind. No performative outrage, no coerced consensus—just a room of unyielding minds who’d traded the illusion of safety for the grit of truth. Four years prior, I’d been alone in my resistance. Now, I raised my glass among my people - those who had seen the system's lies and chosen freedom instead. Each had their own story of awakening, their own battles fought, but here we shared the same hard-won truth.
The energy wasn’t just electric. It was alive—the kind that emerges when free people build rather than beg. For the first time, I didn’t just belong. I was home. And in that moment, the halving’s ticking clock mirrored my own journey: cyclical, predictable in its scarcity, revolutionary in its consequences. Four years had burned away the old world. What remained was stronger.

No Regrets
Leaving the herd wasn’t a choice—it was evolution. My soul shouted: "I’d rather stand alone than kneel with the masses!". The Bitcoin community became more than family; they’re living proof that the world still produces warriors, not sheep. Here, among those who forge truth, I found something extinct elsewhere: hope that burns brighter with every halving, every block, every defiant mind that joins the fight.
Change doesn’t come from the crowd. It starts when one person stops applauding.
Today, I stand exactly where I always wanted to be—shoulder-to-shoulder with my true family: the rebels, the builders, the ungovernable. Together, we’re building the decentralized future.
-
 @ ffbcb706:b0574044
2025-05-13 08:51:07
@ ffbcb706:b0574044
2025-05-13 08:51:07Lorem ipsum dolor sit amet consectetur adipiscing elit. Quisque faucibus ex sapien vitae pellentesque sem placerat. In id cursus mi pretium tellus duis convallis. Tempus leo eu aenean sed diam urna tempor. Pulvinar vivamus fringilla lacus nec metus bibendum egestas. Iaculis massa nisl malesuada lacinia integer nunc posuere. Ut hendrerit semper vel class aptent taciti sociosqu. Ad litora torquent per conubia nostra inceptos himenaeos.
Lorem ipsum dolor sit amet consectetur adipiscing elit. Quisque faucibus ex sapien vitae pellentesque sem placerat. In id cursus mi pretium tellus duis convallis. Tempus leo eu aenean sed diam urna tempor. Pulvinar vivamus fringilla lacus nec metus bibendum egestas. Iaculis massa nisl malesuada lacinia integer nunc posuere. Ut hendrerit semper vel class aptent taciti sociosqu. Ad litora torquent per conubia nostra inceptos himenaeos.
-
 @ 6e0ea5d6:0327f353
2025-04-19 15:09:18
@ 6e0ea5d6:0327f353
2025-04-19 15:09:18🩸
The world won’t stop and wait for you to recover.Do your duty regardless of how you feel. That’s the only guarantee you’ll end the day alright.
You’ve heard it before: “The worst workout is the one you didn’t do.” Sometimes you don’t feel like going to the gym. You start bargaining with laziness: “I didn’t sleep well… maybe I should skip today.” But then you go anyway, committing only to the bare minimum your energy allows. And once you start, your body outperforms your mind’s assumptions—it turns out to be one of the best workouts you’ve had in a long time. The feeling of following through, of winning a battle you were losing, gives you the confidence to own the rest of your day. You finally feel good.
And that wouldn’t have happened if you stayed home waiting to feel better. Guilt would’ve joined forces with discouragement, and you’d be crushed by melancholy in a victim mindset. That loss would bleed into the rest of your week, conditioning your mind: because you didn’t spend your energy on the workout, you’d stay up late, wake up worse, and while waiting to feel “ready,” you’d lose a habit that took months of effort to build.
When in doubt, just do your duty. Stick to the plan. Don’t negotiate with your feelings—outsmart them. “Just one page today,” and you’ll end up reading ten. “Only the easy tasks,” and you’ll gain momentum to conquer the hard ones. Laziness is a serpent—you win when you make no deals with it.
A close friend once told me that when he was at his limit during a second job shift, he’d open a picture on his phone—of a fridge or a stove he needed to buy for his home—and that image gave him strength to stay awake. That moment stuck with me forever.
Do you really think the world will have the same mercy on you that you have on yourself? Don’t be surprised when it doesn’t spare you. Move forward even while stitching your wounds: “If you wait for perfect conditions, you’ll never do anything.” (Ecclesiastes 11:4)
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ eab58da0:eebdafbf
2025-05-13 10:01:07
@ eab58da0:eebdafbf
2025-05-13 10:01:07“Procrastinating is the assassination of all destination.” That hits hard, right? It’s like we’re secretly sabotaging our own dreams, one “I’ll do it later” at a time. Procrastination isn’t just laziness—it’s a sneaky thief that steals momentum and keeps us stuck. Let’s unpack why we procrastinate and how to break free so we can actually get to where we’re headed.
What’s Really Making You Stall Procrastination often comes from fear dressed up as excuses. Maybe it’s fear of failing, looking dumb, or even succeeding and facing new pressures. Sometimes, it’s just overwhelm—tasks feel like mountains, so we freeze. I remember putting off a writing project because I was scared it wouldn’t be “perfect.” The truth? Perfection’s a myth, and waiting for it kills progress. Other times, we procrastinate because we’re distracted or lack clarity on what’s next. Figuring out the “why” behind your delay is the first step to beating it. Ask yourself: What’s holding me back here? Be real—the answer’s usually deeper than “I’m just tired.”
Chopping Big Tasks into Tiny Bits Big goals can feel like monsters, so slice them up. Want to write a book? Don’t stare at the whole thing—commit to 200 words today. Need to declutter your space? Start with one drawer. Breaking tasks into small, doable chunks makes them less intimidating. It’s like tricking your brain into starting. I tried this with a work deadline: instead of stressing over the whole report, I focused on one section at a time. Suddenly, it felt manageable, and I was moving. Set a timer for 10 minutes and just start—momentum will carry you.
Building a Vibe to Get Stuff Done Create a routine that sparks action. Find your sweet spot—maybe it’s a quiet morning with coffee or a playlist that pumps you up. Clear distractions; put your phone in another room if you have to. Reward yourself, too—a quick walk or a treat after finishing a task keeps the vibe positive. Most importantly, tie your work to your “why.” Remind yourself what you’re chasing—freedom, growth, or just peace of mind. That destination is worth fighting for.
Procrastination might try to assassinate your goals, but you’re stronger. Spot the root, break tasks down, and build a routine that pulls you forward. Start small, stay real, and watch how fast you move toward where you’re meant to be.
-
 @ 6e0ea5d6:0327f353
2025-04-19 15:02:55
@ 6e0ea5d6:0327f353
2025-04-19 15:02:55My friend, let yourself be deluded for a moment, and reality will see to it that your fantasy is shattered—like a hammer crushing marble. The real world grants no mercy; it will relentlessly tear down your aspirations, casting them into the abyss of disillusionment and burying your dreams under the unbearable weight of your own expectations. It’s an inescapable fate—but the outcome is still in your hands: perish at the bottom like a wretch or turn the pit into a trench.
Davvero, everyone must eventually face something that breaks them. It is in devastation that man discovers what he is made of, and in the silence of defeat that he hears the finest advice. Yet the weak would rather embrace the convenient lie of self-pity, blaming life for failures that are, in truth, the result of their own negligence and cowardly choices. If you hide behind excuses because you fear the painful truth, know this: the responsibility has always been yours.
Ascolta bene! Just remain steadfast, even when everything feels like an endless maze. The difficulties you face today—those you believe you’ll never overcome—will one day seem insignificant under the light of time and experience. Tomorrow, you’ll look back and laugh at yourself for ever letting these storms seem so overwhelming.
Now, it’s up to you to fight your own battle—for the evil day spares no one. Don’t let yourself be paralyzed by shock or bow before adversity. Be strong and of good courage—not as one who waits for relief, but as one prepared to face the inevitable and turn pain into glory.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ da0b9bc3:4e30a4a9
2025-05-13 09:57:03
@ da0b9bc3:4e30a4a9
2025-05-13 09:57:03Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/978875
-
 @ 57d1a264:69f1fee1
2025-05-13 06:42:47
@ 57d1a264:69f1fee1
2025-05-13 06:42:47Using form, color, typography, and art direction, designers create entire worlds around fragrance – translating scent into sight, touch, and story. But how do you design for something you cannot see? And can design help us smell what we see?
Does design have a smell? While sight, touch, and even taste have long been intertwined with aesthetics, scent remains a more elusive medium – intangible yet profoundly evocative. In a screen-based world, scent has to be seen before it’s smelled – meaning design does more heavy-lifting. Unlike the olden days of magazine inserts spritzed with perfume, scent no longer leads the experience. Instead, branding has to translate fragrance into something we can see, study, and feel. But how do you give form to the formless? Can design make us smell what we see?
Fragrance has always been a playground for aesthetic exploration. Perfume branding has historically been an exercise in worldbuilding; desire is conjured through design. Think of David Lynch’s commercial for YSL’s Opium, a hypnotic fever dream of saturated reds and oranges and surreal imagery, where the perfume becomes almost mythical – more ritual than product. Or take vintage Guerlain ads, whose painterly compositions and opulent typography evoke a world of old-money glamour and whispered intrigue. Here, design and art direction don’t just encode meaning; they heighten the fantasy. The aesthetics transcend the physical product to sell a feeling, an atmosphere – a dream.
Continue reading at https://www.itsnicethat.com/features/designing-for-scent-branding-graphic-design-feature-240425
originally posted at https://stacker.news/items/978832
-
 @ 3ffac3a6:2d656657
2025-04-15 14:49:31
@ 3ffac3a6:2d656657
2025-04-15 14:49:31🏅 Como Criar um Badge Épico no Nostr com
nak+ badges.pageRequisitos:
- Ter o
nakinstalado (https://github.com/fiatjaf/nak) - Ter uma chave privada Nostr (
nsec...) - Acesso ao site https://badges.page
- Um relay ativo (ex:
wss://relay.primal.net)
🔧 Passo 1 — Criar o badge em badges.page
- Acesse o site https://badges.page
-
Clique em "New Badge" no canto superior direito
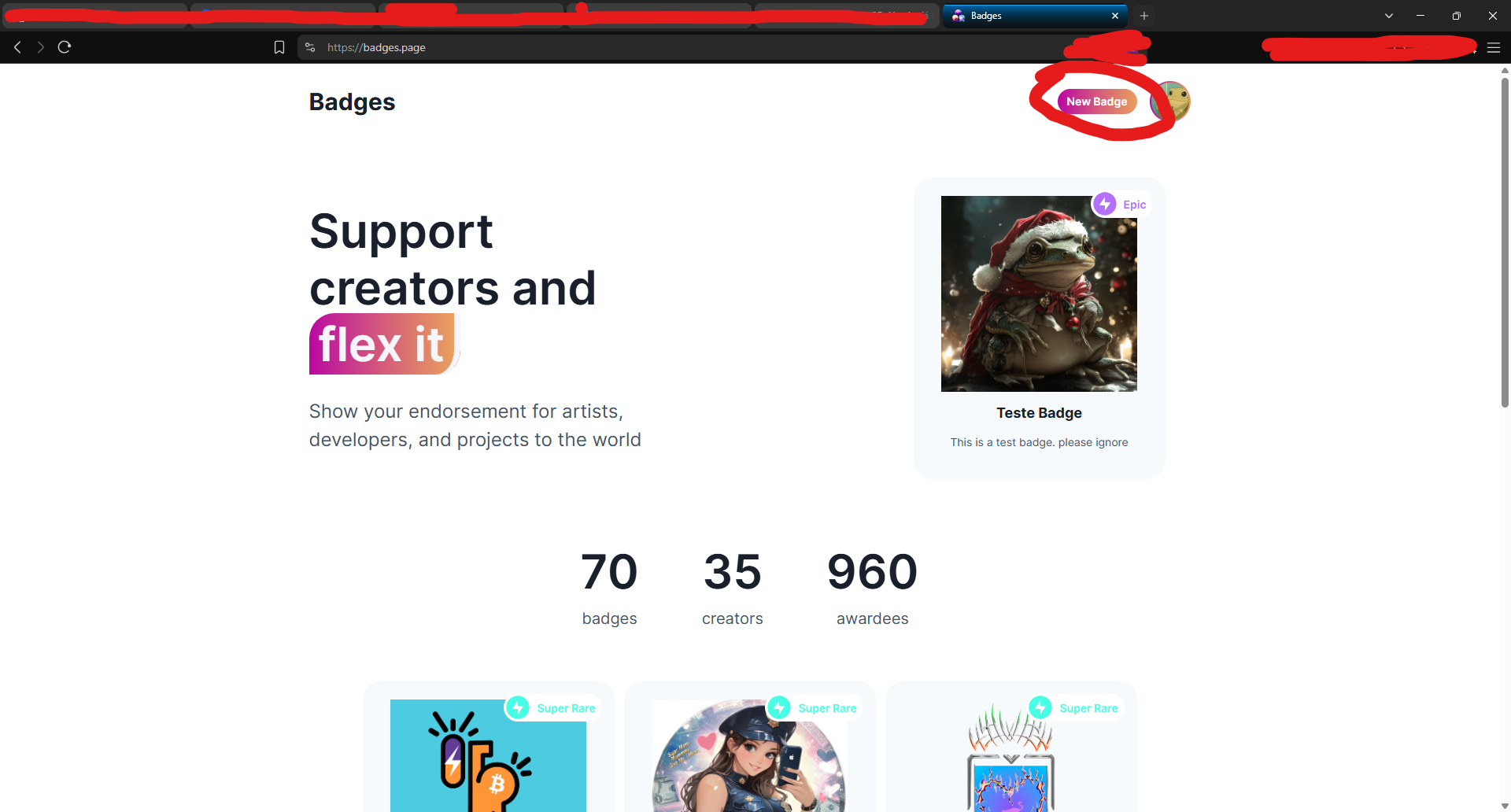
-
Preencha os campos:
- Nome (ex:
Teste Épico) - Descrição
-
Imagem e thumbnail
-
Após criar, você será redirecionado para a página do badge.
🔍 Passo 2 — Copiar o
naddrdo badgeNa barra de endereços, copie o identificador que aparece após
/a/— este é o naddr do seu badge.Exemplo:
nostr:naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Copie:
naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0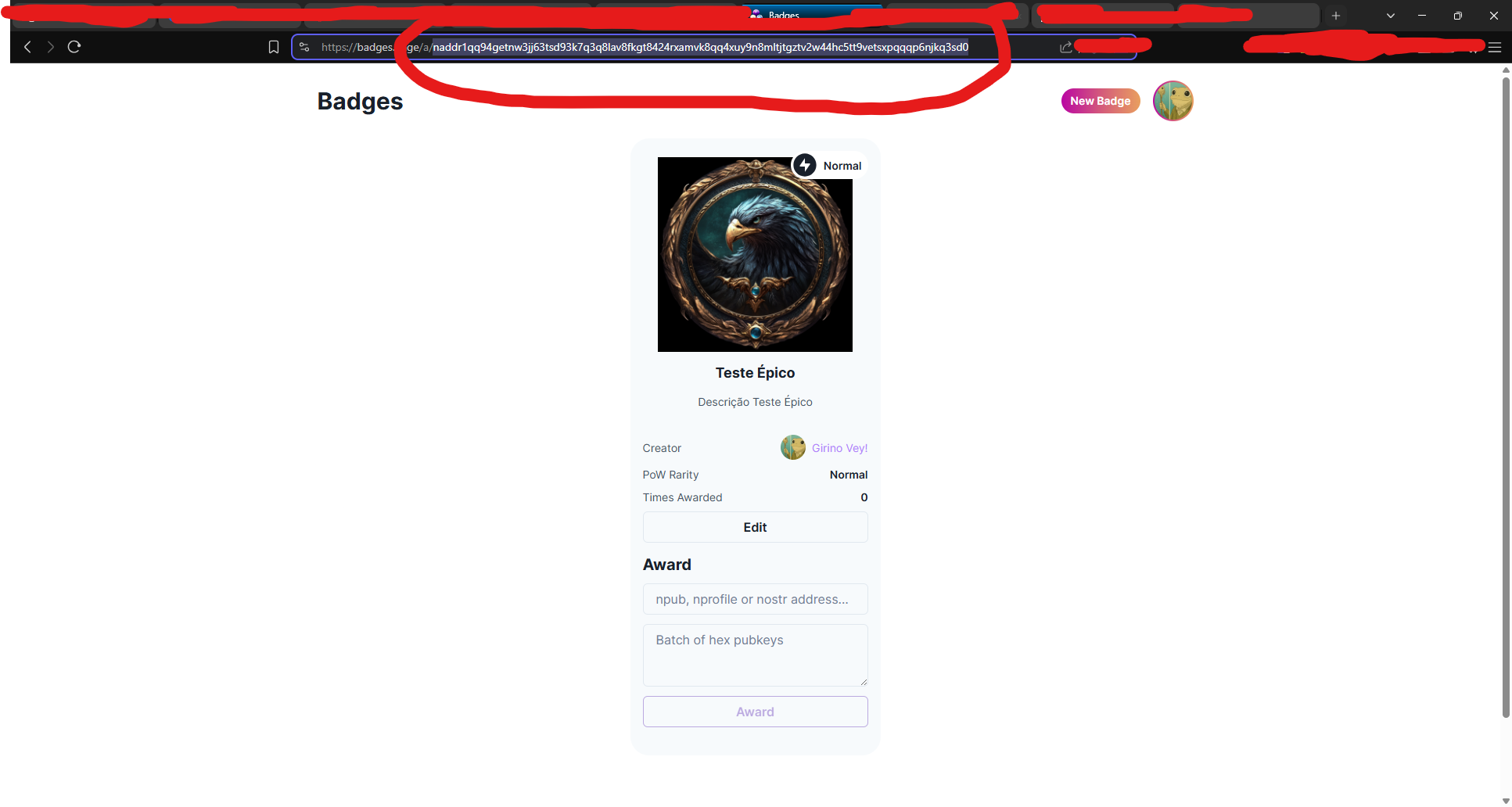
🧠 Passo 3 — Decodificar o naddr com
nakAbra seu terminal (ou Cygwin no Windows) e rode:
bash nak decode naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Você verá algo assim:
json { "pubkey": "3ffac3a6c859eaaa8cdddb2c7002a6e10b33efeb92d025b14ead6f8a2d656657", "kind": 30009, "identifier": "Teste-Epico" }Grave o campo
"identifier"— nesse caso: Teste-Epico
🛰️ Passo 4 — Consultar o evento no relay
Agora vamos pegar o evento do badge no relay:
bash nak req -d "Teste-Epico" wss://relay.primal.netVocê verá o conteúdo completo do evento do badge, algo assim:
json { "kind": 30009, "tags": [["d", "Teste-Epico"], ["name", "Teste Épico"], ...] }
💥 Passo 5 — Minerar o evento como "épico" (PoW 31)
Agora vem a mágica: minerar com proof-of-work (PoW 31) para que o badge seja classificado como épico!
bash nak req -d "Teste-Epico" wss://relay.primal.net | nak event --pow 31 --sec nsec1SEU_NSEC_AQUI wss://relay.primal.net wss://nos.lol wss://relay.damus.ioEsse comando: - Resgata o evento original - Gera um novo com PoW de dificuldade 31 - Assina com sua chave privada
nsec- E publica nos relays wss://relay.primal.net, wss://nos.lol e wss://relay.damus.io⚠️ Substitua
nsec1SEU_NSEC_AQUIpela sua chave privada Nostr.
✅ Resultado
Se tudo der certo, o badge será atualizado com um evento de PoW mais alto e aparecerá como "Epic" no site!
- Ter o
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 57d1a264:69f1fee1
2025-05-13 06:32:15
@ 57d1a264:69f1fee1
2025-05-13 06:32:15You don’t have to be a type designer to appreciate what goes into the design of a letterform. In fact, even if you’re just a humble graphic designer, you should have a basic knowledge of what constructs the type you employ.
Typography, for all its concepts, expectations, implications, connotations and artistry, is, ultimately, a system. Just like a body has bones and muscles, every letterform has parts that give it shape, rhythm, and character.
If you're a creative working with type, learning the names of these parts helps you communicate clearly, better analyze your work and others, and design with precision. Everything comes down to a foundational understanding of the anatomy of the letterform and its essential component. So let’s help you with that.
Pangram Pangram Foundry is where the art of typography meets unparalleled craftsmanship. Established in 2018 by designer Mat Desjardins, Pangram Pangram has swiftly risen to become a globally recognized independent type foundry, admired and trusted by industry peers and the design community alike.
Read more about the anatomy of fonts at https://pangrampangram.com/blogs/journal/anatomy-of-the-letterform
originally posted at https://stacker.news/items/978828
-
 @ c4b5369a:b812dbd6
2025-04-15 07:26:16
@ c4b5369a:b812dbd6
2025-04-15 07:26:16Offline transactions with Cashu
Over the past few weeks, I've been busy implementing offline capabilities into nutstash. I think this is one of the key value propositions of ecash, beinga a bearer instrument that can be used without internet access.
 It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!
It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!What is ecash/Cashu?
Ecash is the first cryptocurrency ever invented. It was created by David Chaum in 1983. It uses a blind signature scheme, which allows users to prove ownership of a token without revealing a link to its origin. These tokens are what we call ecash. They are bearer instruments, meaning that anyone who possesses a copy of them, is considered the owner.
Cashu is an implementation of ecash, built to tightly interact with Bitcoin, more specifically the Bitcoin lightning network. In the Cashu ecosystem,
Mintsare the gateway to the lightning network. They provide the infrastructure to access the lightning network, pay invoices and receive payments. Instead of relying on a traditional ledger scheme like other custodians do, the mint issues ecash tokens, to represent the value held by the users.How do normal Cashu transactions work?
A Cashu transaction happens when the sender gives a copy of his ecash token to the receiver. This can happen by any means imaginable. You could send the token through email, messenger, or even by pidgeon. One of the common ways to transfer ecash is via QR code.
The transaction is however not finalized just yet! In order to make sure the sender cannot double-spend their copy of the token, the receiver must do what we call a
swap. A swap is essentially exchanging an ecash token for a new one at the mint, invalidating the old token in the process. This ensures that the sender can no longer use the same token to spend elsewhere, and the value has been transferred to the receiver.
What about offline transactions?
Sending offline
Sending offline is very simple. The ecash tokens are stored on your device. Thus, no internet connection is required to access them. You can litteraly just take them, and give them to someone. The most convenient way is usually through a local transmission protocol, like NFC, QR code, Bluetooth, etc.
The one thing to consider when sending offline is that ecash tokens come in form of "coins" or "notes". The technical term we use in Cashu is
Proof. It "proofs" to the mint that you own a certain amount of value. Since these proofs have a fixed value attached to them, much like UTXOs in Bitcoin do, you would need proofs with a value that matches what you want to send. You can mix and match multiple proofs together to create a token that matches the amount you want to send. But, if you don't have proofs that match the amount, you would need to go online and swap for the needed proofs at the mint.Another limitation is, that you cannot create custom proofs offline. For example, if you would want to lock the ecash to a certain pubkey, or add a timelock to the proof, you would need to go online and create a new custom proof at the mint.
Receiving offline
You might think: well, if I trust the sender, I don't need to be swapping the token right away!
You're absolutely correct. If you trust the sender, you can simply accept their ecash token without needing to swap it immediately.
This is already really useful, since it gives you a way to receive a payment from a friend or close aquaintance without having to worry about connectivity. It's almost just like physical cash!
It does however not work if the sender is untrusted. We have to use a different scheme to be able to receive payments from someone we don't trust.
Receiving offline from an untrusted sender
To be able to receive payments from an untrusted sender, we need the sender to create a custom proof for us. As we've seen before, this requires the sender to go online.
The sender needs to create a token that has the following properties, so that the receciver can verify it offline:
- It must be locked to ONLY the receiver's public key
- It must include an
offline signature proof(DLEQ proof) - If it contains a timelock & refund clause, it must be set to a time in the future that is acceptable for the receiver
- It cannot contain duplicate proofs (double-spend)
- It cannot contain proofs that the receiver has already received before (double-spend)

If all of these conditions are met, then the receiver can verify the proof offline and accept the payment. This allows us to receive payments from anyone, even if we don't trust them.
At first glance, this scheme seems kinda useless. It requires the sender to go online, which defeats the purpose of having an offline payment system.
I beleive there are a couple of ways this scheme might be useful nonetheless:
-
Offline vending machines: Imagine you have an offline vending machine that accepts payments from anyone. The vending machine could use this scheme to verify payments without needing to go online itself. We can assume that the sender is able to go online and create a valid token, but the receiver doesn't need to be online to verify it.
-
Offline marketplaces: Imagine you have an offline marketplace where buyers and sellers can trade goods and services. Before going to the marketplace the sender already knows where he will be spending the money. The sender could create a valid token before going to the marketplace, using the merchants public key as a lock, and adding a refund clause to redeem any unspent ecash after it expires. In this case, neither the sender nor the receiver needs to go online to complete the transaction.
How to use this
Pretty much all cashu wallets allow you to send tokens offline. This is because all that the wallet needs to do is to look if it can create the desired amount from the proofs stored locally. If yes, it will automatically create the token offline.
Receiving offline tokens is currently only supported by nutstash (experimental).
To create an offline receivable token, the sender needs to lock it to the receiver's public key. Currently there is no refund clause! So be careful that you don't get accidentally locked out of your funds!

The receiver can then inspect the token and decide if it is safe to accept without a swap. If all checks are green, they can accept the token offline without trusting the sender.

The receiver will see the unswapped tokens on the wallet homescreen. They will need to manually swap them later when they are online again.
 Later when the receiver is online again, they can swap the token for a fresh one.
Later when the receiver is online again, they can swap the token for a fresh one.
Summary
We learned that offline transactions are possible with ecash, but there are some limitations. It either requires trusting the sender, or relying on either the sender or receiver to be online to verify the tokens, or create tokens that can be verified offline by the receiver.
I hope this short article was helpful in understanding how ecash works and its potential for offline transactions.
Cheers,
Gandlaf
-
 @ 57d1a264:69f1fee1
2025-05-13 06:21:36
@ 57d1a264:69f1fee1
2025-05-13 06:21:36Steve Jobs sent me an email saying “Great idea, thank you."
Wait, what? What was the great idea?
new guy at NeXT In October of 1991, I was a new Systems Engineer at NeXT. NeXT, of course, was the company Steve Jobs had founded after leaving Apple in 1985, and which eventually merged back into Apple in 1996. I was one of three employees in Canada, and I think NeXT had about 400 people total.
NeXTMail Mail on the NeXT Computer was pretty amazing in 1991. Multimedia! Fonts! Attachments! Sounds! It’s hard to overstate how cool that was compared to the command line email everybody was used to. Every NeXT user got this email from Steve when they started up their computer.
That message included an attachment of what NeXT called Lip Service, the crazy idea that you could embed an audio file inside an email message. Crazy.
i have an idea
NeXT automatically set everybody up with a first-initial last-name address in the usual way, so I was shayman@next.com, and the big guy was sjobs@next.com.
A few colleagues had somehow acquired cooler email aliases - single letter things, or their first name, or a nickname or an easier to spell version, or whatever. Turns out NeXT had set up some sort of form where you could request an email alias that would redirect to whatever your real email address was.
I also noticed that even though there were seven or eight people at NeXT named Steve, nobody was using the email alias steve@next.com.
So late one Friday night, two weeks into the job, I figured, naively, what the heck, nobody else seems to want it, so I filled in the form asking for steve@next.com to be forwarded to me, shayman@next.com.
In the back of my mind was a vague idea that maybe somebody would have to approve this. But no, it all got set up automatically, and …
Continue reading at https://blog.hayman.net/2025/05/06/from-steve-jobs-great-idea.html
originally posted at https://stacker.news/items/978825
-
 @ 266815e0:6cd408a5
2025-04-15 06:58:14
@ 266815e0:6cd408a5
2025-04-15 06:58:14Its been a little over a year since NIP-90 was written and merged into the nips repo and its been a communication mess.
Every DVM implementation expects the inputs in slightly different formats, returns the results in mostly the same format and there are very few DVM actually running.
NIP-90 is overloaded
Why does a request for text translation and creating bitcoin OP_RETURNs share the same input
itag? and why is there anoutputtag on requests when only one of them will return an output?Each DVM request kind is for requesting completely different types of compute with diffrent input and output requirements, but they are all using the same spec that has 4 different types of inputs (
text,url,event,job) and an undefined number ofoutputtypes.Let me show a few random DVM requests and responses I found on
wss://relay.damus.ioto demonstrate what I mean:This is a request to translate an event to English
json { "kind": 5002, "content": "", "tags": [ // NIP-90 says there can be multiple inputs, so how would a DVM handle translatting multiple events at once? [ "i", "<event-id>", "event" ], [ "param", "language", "en" ], // What other type of output would text translations be? image/jpeg? [ "output", "text/plain" ], // Do we really need to define relays? cant the DVM respond on the relays it saw the request on? [ "relays", "wss://relay.unknown.cloud/", "wss://nos.lol/" ] ] }This is a request to generate text using an LLM model
json { "kind": 5050, // Why is the content empty? wouldn't it be better to have the prompt in the content? "content": "", "tags": [ // Why use an indexable tag? are we ever going to lookup prompts? // Also the type "prompt" isn't in NIP-90, this should probably be "text" [ "i", "What is the capital of France?", "prompt" ], [ "p", "c4878054cff877f694f5abecf18c7450f4b6fdf59e3e9cb3e6505a93c4577db2" ], [ "relays", "wss://relay.primal.net" ] ] }This is a request for content recommendation
json { "kind": 5300, "content": "", "tags": [ // Its fine ignoring this param, but what if the client actually needs exactly 200 "results" [ "param", "max_results", "200" ], // The spec never mentions requesting content for other users. // If a DVM didn't understand this and responded to this request it would provide bad data [ "param", "user", "b22b06b051fd5232966a9344a634d956c3dc33a7f5ecdcad9ed11ddc4120a7f2" ], [ "relays", "wss://relay.primal.net", ], [ "p", "ceb7e7d688e8a704794d5662acb6f18c2455df7481833dd6c384b65252455a95" ] ] }This is a request to create a OP_RETURN message on bitcoin
json { "kind": 5901, // Again why is the content empty when we are sending human readable text? "content": "", "tags": [ // and again, using an indexable tag on an input that will never need to be looked up ["i", "09/01/24 SEC Chairman on the brink of second ETF approval", "text"] ] }My point isn't that these event schema's aren't understandable but why are they using the same schema? each use-case is different but are they all required to use the same
itag format as input and could support all 4 types of inputs.Lack of libraries
With all these different types of inputs, params, and outputs its verify difficult if not impossible to build libraries for DVMs
If a simple text translation request can have an
eventortextas inputs, apayment-requiredstatus at any point in the flow, partial results, or responses from 10+ DVMs whats the best way to build a translation library for other nostr clients to use?And how do I build a DVM framework for the server side that can handle multiple inputs of all four types (
url,text,event,job) and clients are sending all the requests in slightly differently.Supporting payments is impossible
The way NIP-90 is written there isn't much details about payments. only a
payment-requiredstatus and a genericamounttagBut the way things are now every DVM is implementing payments differently. some send a bolt11 invoice, some expect the client to NIP-57 zap the request event (or maybe the status event), and some even ask for a subscription. and we haven't even started implementing NIP-61 nut zaps or cashu A few are even formatting the
amountnumber wrong or denominating it in sats and not mili-satsBuilding a client or a library that can understand and handle all of these payment methods is very difficult. for the DVM server side its worse. A DVM server presumably needs to support all 4+ types of payments if they want to get the most sats for their services and support the most clients.
All of this is made even more complicated by the fact that a DVM can ask for payment at any point during the job process. this makes sense for some types of compute, but for others like translations or user recommendation / search it just makes things even more complicated.
For example, If a client wanted to implement a timeline page that showed the notes of all the pubkeys on a recommended list. what would they do when the selected DVM asks for payment at the start of the job? or at the end? or worse, only provides half the pubkeys and asks for payment for the other half. building a UI that could handle even just two of these possibilities is complicated.
NIP-89 is being abused
NIP-89 is "Recommended Application Handlers" and the way its describe in the nips repo is
a way to discover applications that can handle unknown event-kinds
Not "a way to discover everything"
If I wanted to build an application discovery app to show all the apps that your contacts use and let you discover new apps then it would have to filter out ALL the DVM advertisement events. and that's not just for making requests from relays
If the app shows the user their list of "recommended applications" then it either has to understand that everything in the 5xxx kind range is a DVM and to show that is its own category or show a bunch of unknown "favorites" in the list which might be confusing for the user.
In conclusion
My point in writing this article isn't that the DVMs implementations so far don't work, but that they will never work well because the spec is too broad. even with only a few DVMs running we have already lost interoperability.
I don't want to be completely negative though because some things have worked. the "DVM feeds" work, although they are limited to a single page of results. text / event translations also work well and kind
5970Event PoW delegation could be cool. but if we want interoperability, we are going to need to change a few things with NIP-90I don't think we can (or should) abandon NIP-90 entirely but it would be good to break it up into small NIPs or specs. break each "kind" of DVM request out into its own spec with its own definitions for expected inputs, outputs and flow.
Then if we have simple, clean definitions for each kind of compute we want to distribute. we might actually see markets and services being built and used.
-
 @ e7fa8a9e:81ba790d
2025-05-13 08:11:25
@ e7fa8a9e:81ba790d
2025-05-13 08:11:25O 886bet é uma plataforma inovadora que se destaca no universo dos jogos e apostas online, oferecendo uma experiência imersiva e envolvente para os usuários que buscam diversão e emoção. Com uma vasta gama de opções e recursos, o 886bet é o destino perfeito para quem deseja se divertir com jogos emocionantes e uma interface amigável. Neste artigo, vamos explorar o que torna o 886bet único, desde sua apresentação até a experiência do jogador, passando pelas incríveis opções de jogos que a plataforma oferece.
Uma Plataforma Fácil de Navegar e Segura O 886bet foi desenvolvido com o intuito de proporcionar uma experiência de usuário sem fricções. A plataforma possui uma interface moderna, intuitiva e de fácil navegação, permitindo que até mesmo os novatos se sintam confortáveis ao acessar seus jogos favoritos. Seu design responsivo se adapta perfeitamente a diferentes dispositivos, seja no desktop ou no celular, garantindo que a diversão esteja sempre ao alcance de todos, em qualquer lugar.
Além disso, a segurança é uma prioridade no 886bet. A plataforma investe constantemente em tecnologias de criptografia de ponta, garantindo que as informações pessoais e financeiras dos jogadores sejam mantidas em sigilo absoluto. Com um compromisso claro com a privacidade, os usuários podem se concentrar apenas na diversão, sem preocupações extras.
Diversão Garantida com uma Variedade de Jogos O 886bet oferece uma vasta seleção de jogos, atendendo a uma diversidade de gostos e preferências. Desde os jogos de mesa mais tradicionais até as mais modernas opções de jogos de habilidade, todos os tipos de jogadores podem encontrar algo que combine com seu estilo. A plataforma é constantemente atualizada com novos títulos, garantindo que sempre haja algo novo e emocionante para explorar.
Jogos de Mesa Para os fãs dos jogos de mesa, o 886bet oferece uma variedade de opções que vão desde os tradicionais jogos de cartas até as versões mais inovadoras. Os jogadores podem experimentar diferentes variações de jogos como blackjack, roleta e baccarat, com regras claras e opções para iniciantes e jogadores mais experientes. A qualidade dos gráficos e a fluidez do jogo proporcionam uma experiência realista e divertida, que transporta o jogador para um ambiente dinâmico e envolvente.
Jogos de Habilidade Além dos jogos de mesa, a plataforma também oferece opções para aqueles que desejam testar suas habilidades. Jogos como pôquer, que exigem estratégia e tomada de decisão, estão disponíveis em várias modalidades, permitindo aos jogadores aprimorar suas táticas e competir contra outros usuários em tempo real.
Jogos ao Vivo Para quem busca uma experiência mais interativa e imersiva, o 886bet oferece jogos ao vivo, onde os jogadores podem competir contra dealers reais em tempo real. Esta opção proporciona uma atmosfera vibrante e autêntica, mais próxima de uma experiência física, com a vantagem de ser jogado no conforto de casa.
A Experiência do Jogador: Conforto, Prêmios e Suporte No 886bet, o jogador sempre estará no centro da experiência. A plataforma foi desenvolvida para garantir uma navegação fluida e sem interrupções, com transações rápidas e seguras. A experiência do jogador é enriquecida com promoções regulares, bônus atrativos e torneios exclusivos que oferecem a chance de ganhar prêmios e recompensas interessantes.
Além disso, o 886bet oferece suporte ao cliente 24/7, para que os jogadores possam resolver qualquer dúvida ou problema que surja de maneira rápida e eficiente. O atendimento ao cliente é realizado por meio de diversos canais, incluindo chat ao vivo e e-mail, proporcionando um serviço de alta qualidade sempre que necessário.
Conclusão: A Escolha Perfeita para Entretenimento Online O 886bet se destaca como uma plataforma completa de entretenimento online, oferecendo uma enorme variedade de jogos e recursos para os jogadores. Com uma interface intuitiva, segurança de alto nível e uma vasta gama de opções de jogos, o 886bet proporciona uma experiência única e personalizada. Seja você um jogador novato ou experiente, a plataforma atende a todas as suas necessidades e garante horas de diversão e emoção. Se você está procurando por uma plataforma de entretenimento online de alta qualidade, o 886beté, sem dúvida, uma das melhores opções disponíveis.
-
 @ e7fa8a9e:81ba790d
2025-05-13 08:09:55
@ e7fa8a9e:81ba790d
2025-05-13 08:09:55A 1848Bet é uma plataforma de jogos online que tem se destacado por oferecer uma experiência única e de alta qualidade aos seus usuários. Com uma vasta gama de jogos e recursos inovadores, a 1848Bet se posiciona como uma das principais opções para aqueles que buscam diversão, segurança e facilidade na hora de jogar. Neste artigo, vamos explorar os aspectos que tornam a 1848Bet uma escolha excelente para os jogadores, desde sua introdução até a experiência que ela proporciona.
Uma Plataforma de Entretenimento de Alta Qualidade A 1848Bet foi criada para oferecer uma experiência de jogo online sem igual. Sua plataforma é totalmente otimizada para garantir acessibilidade e conveniência, seja para quem está começando a explorar o universo dos jogos online ou para jogadores experientes em busca de novos desafios. A interface é moderna, intuitiva e muito fácil de navegar, o que garante que qualquer pessoa, independentemente de seu nível de experiência, possa desfrutar dos jogos com facilidade.
Além disso, a plataforma é 100% compatível com dispositivos móveis, permitindo que os jogadores acessem seus jogos favoritos de qualquer lugar e a qualquer momento. A 1848Bet se compromete a manter sua plataforma segura e confiável, oferecendo criptografia de ponta para garantir a proteção dos dados dos usuários.
Jogos para Todos os Gostos Na 1848Bet, os jogadores têm à disposição uma vasta seleção de jogos, que inclui desde opções clássicas até as mais modernas e inovadoras. Com uma grande variedade de opções, a plataforma se garante como um ambiente de entretenimento diversificado, ideal para todos os tipos de jogadores.
Entre os jogos disponíveis, destacam-se as opções de esportes virtuais, onde os jogadores podem participar de competições em uma série de modalidades. Isso permite aos jogadores viver a emoção de grandes torneios e partidas, com a mesma intensidade e diversão que um evento esportivo real proporciona.
Os jogos de mesa, como roleta e blackjack, são outros grandes atrativos da 1848Bet. Com gráficos impressionantes e uma jogabilidade fluida, essas opções oferecem uma experiência imersiva para aqueles que preferem jogos de estratégia e habilidade. Além disso, a plataforma também oferece uma variedade de slots, com temas e características que atendem a todos os gostos e preferências.
Experiência do Jogador: Conforto, Diversão e Segurança A experiência do jogador na 1848Bet é cuidadosamente planejada para garantir o máximo de satisfação. Desde o momento em que o usuário acessa a plataforma, é possível perceber o compromisso da empresa em oferecer uma jornada de jogo sem complicações e repleta de diversão. O site carrega rapidamente, e o layout intuitivo facilita a navegação, permitindo que o jogador encontre rapidamente os jogos de sua preferência.
A 1848Bet também se destaca por seu excelente suporte ao cliente. A plataforma conta com uma equipe de atendimento pronta para solucionar qualquer dúvida ou problema, seja por chat ao vivo, e-mail ou telefone. Isso proporciona aos jogadores uma sensação de segurança, sabendo que podem contar com a ajuda de profissionais capacitados sempre que necessário.
Outro ponto importante é a possibilidade de realizar transações seguras e rápidas. A 1848Bet oferece diversos métodos de pagamento, incluindo opções populares como cartões de crédito e carteiras digitais, permitindo que os jogadores façam depósitos e retiradas de maneira simples e sem complicações.
Conclusão Com uma plataforma fácil de usar, uma grande variedade de jogos e uma experiência de jogador excepcional, a 1848Bet se posiciona como uma das melhores opções para quem busca entretenimento online de qualidade. Seja você um novato ou um veterano no mundo dos jogos, a 1848Bet oferece tudo o que você precisa para aproveitar ao máximo sua jornada. Se você ainda não conheceu a plataforma, não perca mais tempo e descubra tudo o que ela tem a oferecer!
-
 @ bbef5093:71228592
2025-05-13 04:18:45
@ bbef5093:71228592
2025-05-13 04:18:45Nukleáris politika – 2025. május 12. | Szerző: David Dalton
Lengyelország és Franciaország nukleáris szerződést ír alá, Macron új építési szerződéseket céloz
Lengyelország és Franciaország olyan szerződést kötött, amely együttműködést irányoz elő a polgári nukleáris energia szektorban, miközben Párizs reménykedik abban, hogy Varsótól jövedelmező új atomerőmű-építési szerződéseket nyer el.
A szerződés közös tevékenységeket tartalmaz, amelyek célja a nukleáris energia előnyeinek kihasználása az európai ipar dekarbonizációja érdekében.
A két ország együtt kíván működni a nukleáris fűtőanyag-ellátás biztonságának megerősítésében is.
Európa szeretné kizárni Oroszországot a nukleáris fűtőanyag-piacáról, de az Euratom Ellátási Ügynökség (ESA) legfrissebb éves jelentése szerint 2023-ban nőtt az Oroszországból származó természetes urán szállítása, mivel az uniós szolgáltatók készleteket halmoztak fel az orosz tervezésű VVER atomerőművekhez.
Az ESA, amely az európai nukleáris anyagok rendszeres és méltányos ellátásáért felelős, közölte, hogy az uniós szolgáltatók tovább diverzifikálják nukleáris fűtőanyag-beszerzéseiket, különösen a VVER reaktorokhoz, hogy csökkentsék a „egy forrásból származó vagy magas kockázatú” ellátásoktól való függést.
„Majdnem minden olyan ország, amely orosz tervezésű reaktorokat üzemeltet, halad az alternatív fűtőanyagok engedélyeztetésében, és ígéretes fejlemények várhatók a közeljövőben” – közölte az ESA.
Az EU-ban jelenleg 19 VVER reaktor működik, köztük négy 1000 MW-os Bulgáriában és Csehországban, valamint tizenöt 440 MW-os Csehországban, Finnországban, Magyarországon és Szlovákiában.
A jelentések szerint a francia–lengyel nukleáris szerződés különösen fontos a francia állami EDF energetikai vállalat számára, amely még mindig reménykedik abban, hogy részt vehet Lengyelország ambiciózus atomerőmű-építési programjában, annak ellenére, hogy az első új építésű projekt tenderét az amerikai Westinghouse nyerte el Pomeránia északi tartományában.
Franciaország ambiciózus reaktorépítési tervei
Franciaország maga is nagyszabású nukleáris fejlesztési terveket dédelget: a kormány nemrégiben felkérte az EDF-et, hogy gyorsítsa fel a hat új generációs EPR2 atomerőmű megépítésének előkészítését.
Az EDF kezdetben három EPR2 párost tervez: az elsőt Penlyben, majd egyet-egyet a Gravelines-i atomerőmű telephelyén (Calais közelében), illetve vagy Bugey-ben (Lyon keleti részén), vagy Tricastinban (Lyon és Avignon közelében).
A nukleáris szerződés aláírását megelőzte egy másik szerződés is, amely a két szövetséges közötti kapcsolatok elmélyítését, valamint kölcsönös biztonsági garanciákat is tartalmaz háború esetére.
Donald Tusk lengyel miniszterelnök, aki Emmanuel Macron francia elnökkel együtt írta alá a biztonsági dokumentumot, „áttörésnek” nevezte a szerződést, kiemelve, hogy csak Németországnak van hasonló biztonsági paktuma Franciaországgal, és ez Lengyelországot „egyenrangú partnerként” helyezi nyugati szövetségesei közé.
Macron eközben úgy fogalmazott, hogy a szerződés „új korszakot nyit” nemcsak Lengyelország és Franciaország, hanem egész Európa számára. „Bresttől Krakkóig Európa együtt áll ki” – mondta a francia elnök.
Nukleáris politika – 2025. május 12. | Szerző: David Dalton
Trump csapata a nukleáris erőművek építésének felgyorsítását tervezi
A Trump-adminisztráció tisztviselői végrehajtási rendeleteket készítenek elő, amelyek célja az atomerőművek jóváhagyásának és építésének felgyorsítása az Egyesült Államokban – számolt be róla a sajtó.
Az erőfeszítés, amelyet egy kormányzati tisztviselő és más, az egyeztetéseket ismerő személyek írtak le, még folyamatban van. Az elnök még nem hagyta jóvá a tervezetet – mondta az egyik forrás, aki névtelenséget kért, mivel hivatalos bejelentés még nem történt. Az amerikai Axios hírportál és a New York Times is beszámolt az egyeztetésekről.
Trump és kormányának tisztviselői többször hangsúlyozták a bőséges, olcsó villamos energia fontosságát az energiaigényes mesterséges intelligencia ipar számára, amely segítheti az Egyesült Államokat abban, hogy megnyerje a feltörekvő technológia globális versenyét.
„Meg kell nyernünk az MI-versenyt, és ebben vezetnünk kell – ehhez pedig sokkal több energiára lesz szükség” – mondta Chris Wright energiaügyi miniszter múlt hónapban egy kabinetülésen Trump társaságában.
Az elnök már hivatalosan is energia-vészhelyzetet hirdetett, nemzeti és gazdasági biztonsági szempontokra hivatkozva annak érdekében, hogy gyorsítsa az erőművek, csővezetékek és elektromos távvezetékek építését az országban.
A szóban forgó tervezetek célokat tűznének ki az atomerőművek gyors országos építésére, illetve az amerikai nukleáris ipar vezető szerepének visszaállítására.
Legalább az egyik intézkedés a Nukleáris Szabályozási Bizottságnál (NRC) vezetne be változtatásokat, amelyek gyorsíthatják az erőműtervek, köztük az új kis moduláris reaktorok (SMR-ek) engedélyezését.
Wright nemrégiben úgy nyilatkozott, hogy az új reaktorblokkok építésének legnagyobb akadálya az Egyesült Államokban a szabályozás volt.
Az elképzelés részeként akár katonai létesítményekre is telepíthetnek majd atomerőműveket, valószínűleg mikroreaktorok vagy SMR-ek formájában.
Jelenleg az Egyesült Államokban nincs kereskedelmi atomerőmű építés alatt. Az utolsó két üzembe helyezett blokk a georgiai Vogtle-3 és Vogtle-4 volt, 2023-ban és 2024-ben.
Előrehaladott tervek vannak a michigani Palisades atomerőmű újraindítására. Ha megvalósul, ez lenne az első olyan, korábban leállított amerikai atomerőmű, amely ismét működésbe lép.
Új építések – 2025. május 12. | Szerző: David Dalton
Vietnam és Oroszország tárgyalásokat kezd atomerőmű-építésről
Vietnam és Oroszország megállapodott abban, hogy tárgyalásokat folytatnak és szerződéseket írnak alá kereskedelmi atomerőművek építéséről Vietnamban – közölték a két ország egy közös nyilatkozatban.
„Az erőművek fejlesztése korszerű technológiával szigorúan megfelel majd a nukleáris és sugárbiztonsági előírásoknak, és a társadalmi-gazdasági fejlődést szolgálja” – áll a közleményben, amely a vietnami vezető, To Lam moszkvai látogatása után jelent meg.
Az orosz állami atomenergetikai vállalat, a Roszatom szerint a látogatás „az együttműködés új szakaszát” jelenti – egy nagy atomerőmű építését Délkelet-Ázsiában.
A Roszatom felajánlotta Vietnámnak a VVER-1200 nyomottvizes reaktor technológiáját, amelyből kettő már működik az oroszországi Novovoronyezs 2 atomerőműben, és kettő Fehéroroszországban.
A Roszatom közölte, hogy további tárgyalásokra van szükség a vietnami atomerőmű műszaki és pénzügyi feltételeinek tisztázásához, de hozzátette: „ezek a tárgyalások ma [május 10-én] megkezdődtek”.
A Roszatom arról is beszámolt, hogy Alekszej Lihacsov vezérigazgató és Nguyen Manh Hung vietnami tudományos és technológiai miniszter aláírt egy nukleáris energia ütemtervet.
Az ütemterv tartalmazza egy nukleáris tudományos és technológiai központ lehetséges megépítését, fűtőanyag-szállítást a dél-vietnami Dalat kutatóreaktorhoz, Vietnam részvételét Oroszország IV. generációs MBIR többcélú gyorsneutronos kutatóreaktor projektjében, valamint vietnami szakemberek képzését.
Vietnamnak jelenleg egy kutatóreaktora van Dalatban, és egy másik is tervben van. A Roszatom nem közölte, melyikre gondolt.
A múlt hónapban Vietnam elfogadta a nemzeti energiastratégia módosított változatát, amely 2030-ig 136 milliárd dollárt irányoz elő az energiaellátás hosszú távú biztonságának megerősítésére, és először szerepel benne az atomenergia.
Vietnam azt szeretné, ha első atomerőművei 2030 és 2035 között lépnének üzembe. A beépített nukleáris kapacitás várhatóan 4–6,4 GW lesz, ami körülbelül 4–6 nagy atomerőműnek felel meg.
A kormány szerint további 8 GW nukleáris kapacitás kerül majd a mixbe az évszázad közepéig.
Vietnam már 2009-ben is tervezett két atomerőművet, de a Nemzetgyűlés 2016-ban költségvetési okokból elutasította a javaslatot.
Új építések – 2025. május 12. | Szerző: David Dalton
Az NRC engedélyt adott az „energia-sziget” munkálatokra a TerraPower wyomingi atomerőművénél
Az Egyesült Államok Nukleáris Szabályozási Bizottsága (NRC) mentességet adott a TerraPower Natrium demonstrációs atomerőművének wyomingi Kemmererben, lehetővé téve a vállalat számára bizonyos „energia-sziget” tevékenységek folytatását, miközben a hatóságok tovább vizsgálják az építési engedély iránti kérelmet.
Az energia-sziget a tervezett Natrium atomerőműben a felesleges hő tárolására szolgál majd, hogy csúcsterhelés idején növelje az áramtermelést.
Az NRC szerint az energia-szigethez kapcsolódó bizonyos tevékenységek engedélyezése nem jelent indokolatlan kockázatot a közegészségre és biztonságra, és „különleges körülmények” állnak fenn.
A mentesség a létesítmények, rendszerek és komponensek korlátozott részére vonatkozik, lehetővé téve például cölöpverést, alapozást, vagy bizonyos szerkezetek, rendszerek és komponensek összeszerelését, gyártását, tesztelését korlátozott munkavégzési engedély nélkül.
Az NRC szerint a mentesség nem befolyásolja a reaktor építési engedélyéről szóló végső döntést. „Az NRC folytatja az építési engedély iránti kérelem vizsgálatát az egész projektre vonatkozóan” – áll a közleményben.
A Bill Gates által alapított TerraPower üdvözölte a döntést, hozzátéve, hogy a nukleáris reaktor és az energiatermelő létesítmények szétválasztása rövidebb építési időt és alacsonyabb anyagköltségeket tesz lehetővé.
Februárban az amerikai energiaügyi minisztérium befejezte a projekt előzetes tevékenységeire vonatkozó végső környezeti értékelést.
A TerraPower, amelyet Gates 2008-ban alapított, 2024 júniusában kezdte meg első kereskedelmi Natrium atomerőművének építését Kemmererben, ahol egy széntüzelésű erőmű zár be.
A Natrium demonstrációs projekt három különálló részből áll: egy nátrium teszt- és feltöltő létesítményből, az energiatermelő vagy energia-szigetből, valamint a nukleáris szigetből magával a reaktorral.
A kezdeti építkezés a teszt- és feltöltő létesítményre összpontosít, amely egy különálló, nem nukleáris épület, és a reaktor nátrium hűtőrendszerének tesztelésére szolgál. Itt történik a folyékony nátrium fogadása, mintavételezése, feldolgozása és tárolása, mielőtt a Natrium reaktorhoz kerülne.
Egyéb hírek
A lengyel atomerőmű-projekt biztosítási szerződéseket kötött
A lengyel Polskie Elektrownie Jądrowe (PEJ) atomerőmű-projekt vállalat négy biztosítási bróker céggel kötött keretmegállapodást. Az Aon Polska, GrECo Polska, Marsh és Smartt Re cégek támogatják a PEJ-t Lengyelország első kereskedelmi atomerőművének biztosítási szerződéseinek megkötésében, valamint a napi működéshez szükséges biztosítások beszerzésében. A PEJ minden brókerrel keretmegállapodást írt alá, amelyek alapján egyes biztosítási feladatokra kiválasztja a megfelelő brókert.
Az Aecon cég nyerte az ontariói SMR építési szerződését
A kanadai Aecon Kiewit Nuclear Partners nyerte el az Ontario Power Generation (OPG) által Darlingtonban építendő első kis moduláris reaktor (SMR) kivitelezési szerződését. A szerződés értéke 1,3 milliárd kanadai dollár (934 millió USD, 841 millió euró), amely projektmenedzsmentet, kivitelezési tervezést és végrehajtást foglal magában, a befejezést és a kereskedelmi üzemet 2030-ra tervezik. Ontario tartomány és az OPG múlt héten hagyta jóvá a négy SMR első darabjának 20,9 milliárd CAD értékű tervét Darlingtonban.
26 000 dolgozó a Hinkley Point C projekten a csúcskivitelezés idején
Az Egyesült Királyságban mintegy 26 000 dolgozó vesz részt a Hinkley Point C atomerőmű építésében, amely jelenleg csúcskivitelezési szakaszban van – derül ki az EDF Energy jelentéséből. Közvetlenül a projekten 18 000-en dolgoznak, ebből 12 000-en a helyszínen, további 3 000 fővel bővülhet a létszám a következő 12 hónapban. További 8 000-en a beszállítói láncban dolgoznak. A jelentés szerint a Hinkley Point C építése fontos katalizátor a gazdasági növekedésben, jelenleg 13,3 milliárd fonttal (15,7 milliárd euró, 17,5 milliárd dollár) járul hozzá a gazdasághoz. Ebből 5 milliárd fontot már a délnyugati régió beszállítóinál költöttek el – jóval meghaladva az 1,5 milliárd fontos célt. A Hinkley Point C két francia EPR reaktort kap.
Az Ansaldo Nucleare nukleáris mesterszakot indít Olaszországban
Az olasz Ansaldo Nucleare és a Politecnico di Milano vállalati mesterszakot indít, amely a nukleáris energia és kapcsolódó technológiák új szakértő generációját képzi. A képzés októberben indul, egy évig tart, 1500 órás, mérnöki, fizikai és kémiai diplomásoknak szól. Húsz résztvevőt választanak ki a következő hónapokban, akiket az Ansaldo Nucleare azonnal, határozatlan időre alkalmaz, és október elején kezdik meg a képzést.
-
 @ 75869cfa:76819987
2025-05-13 03:26:29
@ 75869cfa:76819987
2025-05-13 03:26:29GM, Nostriches!
The Nostr Review is a biweekly newsletter focused on Nostr statistics, protocol updates, exciting programs, the long-form content ecosystem, and key events happening in the Nostr-verse. If you’re interested, join me in covering updates from the Nostr ecosystem!
Quick review:
In the past two weeks, Nostr statistics indicate over 211,000 daily trusted pubkey events. The number of new users has seen a notable decrease, Profiles with contact lists were representing a 50% decline. More than 5 million events have been published, reflecting a 34% decrease. Total Zap activity stands at approximately 14 million, marking a 12% increase.
Additionally, 25 pull requests were submitted to the Nostr protocol, with 8 merged. A total of 60 Nostr projects were tracked, with 18 releasing product updates, and over 356 long-form articles were published, 36% focusing on Bitcoin and Nostr. During this period, 5 notable events took place, and 2 significant events are upcoming.
Nostr Statistics
Based on user activity, the total daily trusted pubkeys writing events is about 211,000, representing a slight 2.7 % decrease compared to the previous period. Daily activity peaked at 17027 events, with a low of approximately 15340.
The number of new users has decreased significantly.Profiles with contact lists were 12961, representing a decline of approximately 50% compared to the previous period. The number of profiles with bios and pubkey-written events remained stable.
The total number of note events published is around 5 million, reflecting a 34% decrease.Posts remain the most dominant category by volume, representing a 9% decrease compared to the previous period.
For zap activity, the total zap amount is about 14 million, showing an decrease of over 12% compared to the previous period.
Data source: https://stats.nostr.band/
NIPs
Introduce NIP-PNS: Private Note Storage #1893
nostr:npub1xtscya34g58tk0z605fvr788k263gsu6cy9x0mhnm87echrgufzsevkk5s is proposing PNS that empowers Nostr users with a secure and seamless way to store personal notes—like diaries, drafts, or private application settings—across devices while keeping them completely private. Built on client-side encryption, PNS ensures that only the user can read or manage their notes, even as they sync effortlessly via Nostr relays. Unlike traditional local storage or cumbersome encrypted file solutions, PNS offers privacy without sacrificing convenience, using deterministic keys tied to each user or device. It integrates directly with Nostr’s open infrastructure, enabling private data to coexist with public events—secure, synchronized, and under your control.
Create 97.md: Ring Signatures #1894
nostr:npub1u5njm6g5h5cpw4wy8xugu62e5s7f6fnysv0sj0z3a8rengt2zqhsxrldq3 is proposing a PR that ring signatures can be synergistic with other web of trust related tools.
Introduce NIP: Relay metadata propagation #1900
nostr:npub1txukm7xckhnxkwu450sm59vh2znwm45mewaps4awkef2tvsgh4vsf7phrl is proposing a simple propagation mechanism for kind:0 (user metadata) and kind:10002 (relay list metadata) events between relays. Relays are allowed to forward such events to their peers, improving client synchronization.
nostr:npub1gzuushllat7pet0ccv9yuhygvc8ldeyhrgxuwg744dn5khnpk3gs3ea5ds defines a standardized interaction pattern for Nostr Data Vending Machines (DVMs). It focuses on how clients discover DVM capabilities, request jobs, and receive results. This NIP decouples the core DVM interaction from specific job-type implementations, which should be defined in separate documents.
NIP-47 Add Hold Invoice Support #1913
frnandu is proposing PR that introduces support for hold invoices in the Nostr Wallet Connect (NIP-47) protocol.Hold invoices enable more advanced payment workflows where the receiver must explicitly settle or cancel the invoice using the preimage. This allows for enhanced control and coordination in payment flows, such as conditional payments or escrow-like behavior.
Add A Generic Raitng/Review NIP #1914
nostr:npub1cgd35mxmy37vhkfcmjckk9dylguz6q8l67cj6h9m45tj5rx569cql9kfex is proposing generic nip that meant to handle all categories of things via namespaced Ids.
Notable Projects
Coracle 0.6.15 nostr:npub13myx4j0pp9uenpjjq68wdvqzywuwxfj64welu28mdvaku222mjtqzqv3qk
New version of Coracle is out: 0.6.15 — this one is just more QoL improvements and bugfixes — the big one this time is better blossom support (and dropping nip 96!). * Fix safe areas more * Improve remote signing * Drop nip 96 support * Use user blossom servers * Improve profile edit page * Avoid duplicate notes in feeds
Flotilla nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn
New version of Flotilla is out as well — 1.0.2 is mostly cleanup from the 1.0 release earlier this week. * Fix add relay button * Fix safe inset areas * Better rendering for errors from relays * Improve remote signer login
Damus Notedeck Beta nostr:npub18m76awca3y37hkvuneavuw6pjj4525fw90necxmadrvjg0sdy6qsngq955
New in Notedeck Beta: * Dave nostr ai assistant app * GIFs! * Fulltext note search * Add full screen images, add zoom & pan * Zaps! NWC/ Wallet ui * Introduce last note per pubkey feed (experimental) * Allow multiple media uploads per selection * Major Android improvements (still wip) * Added notedeck app sidebar * User Tagging * Note truncation * Local network note broadcast, broadcast notes to other notedeck notes while you're offline * Mute list support (reading) * Relay list support * Ctrl-enter to send notes * Added relay indexing (relay columns soon) * Click hashtags to open hashtag timeline
Primal V2.2 nostr:npub12vkcxr0luzwp8e673v29eqjhrr7p9vqq8asav85swaepclllj09sylpugg
Version 2.2 is now live, bringing long-awaited features like Amber signing support and much more. Here’s what’s new: * Blossom media * Push notifications * Notifications overhaul * External signer support * Feed: image gallery revamp * Muted words, hashtags, & threads * Request delete for notes and articles * System photos: share via Primal
Nostur nostr:npub1n0stur7q092gyverzc2wfc00e8egkrdnnqq3alhv7p072u89m5es5mk6h0
New in this version: * Add blossom media server support * Support multiple blossom servers as mirror * Fixed feed position reset on audio bar toggle * Fixed post screenshot broken for quoted posts
Fountain 1.2 nostr:npub1v5ufyh4lkeslgxxcclg8f0hzazhaw7rsrhvfquxzm2fk64c72hps45n0v5
Fountain 1.2 is live on iOS and Android This massive update brings significant design and UX improvements across the app along with new episode summaries features. Here's what's new: * Library Design Update: Fountain has made it much easier to navigate between podcasts and music in the library with the addition of new content-type filters. The Recently Played view allows users to quickly jump back into what they were listening to before, and the design of the content cards has also been refreshed. * Content Pages Design Update: All content pages—including shows, episodes, artists, albums, tracks, clips, and playlists—have undergone an extensive redesign. The previous tab layout has been replaced with scrollable pages, show notes formatting has been improved, and features like chapters and transcripts have been revamped. * Episode Summaries: Each episode page now features a Summary button above the show notes. Users can pay 500 sats to unlock a summary or upgrade to Fountain Premium for $2.99/month to enjoy unlimited summaries. Summaries and transcripts are now bundled together, and they’re faster, cheaper, and more accurate than ever before. * Playback Improvements: The audio engine has been completely rebuilt from the ground up. Playback is now more robust and reliable—especially for music. Tracks now play instantly when tapped, and users can skip seamlessly between tracks in albums and playlists. The player interface has also been updated for easier access to show notes, comments, transcripts, and chapters, with the addition of a smart resume feature for podcasts.
DEG Mods nostr:npub17jl3ldd6305rnacvwvchx03snauqsg4nz8mruq0emj9thdpglr2sst825x
- New Events Aggregator Server, a type of aggregate/caching server that helps collect and organize mod and blog posts from the (nostr) network and presents them to the user, providing more (immensely more) reliability in discovering and presenting mods and blog posts.
- Adjusted how the mods and blogs are fetched and presented in various pages (there's now pagination for each of their pages, making navigation easier than before).
- Minor adjustment to the design of the gallery of mod posts.
- Images in a social post (in /feed) are now clustered depending on if they're next to each other.
- Quote-repost chain won't render its preview with the second quote-repost (under the posts tab in the feed page).
- Added media upload to the edit profile page.
- The games page now has a filter to switch between popular ones (shows the most popular games first based on mods published to it) or latest ones (shows games based on the latest published mods).
- Mods that are blocked by the user are now swapped with a box telling the user this is a blocked mod by them, with an option to see what that mod is.
- Mods can now be properly discovered, as soon as they're discovered, and presented (Because of that aggregate server implementation).
- A lot more games, with better search term prioritization, are now properly showing when searching in the mod submission page
- Visiting a social post directly is now visible without needing to login
RUNSTR nostr:npub1vygzr642y6f8gxcjx6auaf2vd25lyzarpjkwx9kr4y752zy6058s8jvy4e
- Record your cardio and post to nostr
- Save your stats to nostr
- Listen to your nostr:npub1yfg0d955c2jrj2080ew7pa4xrtj7x7s7umt28wh0zurwmxgpyj9shwv6vg playlists and zap your favorite artists
- Interact with the Kind1 RUNSTR Feed
- Interact with NIP29 run clubs
nostr:npub17h9fn2ny0lycg7kmvxmw6gqdnv2epya9h9excnjw9wvml87nyw8sqy3hpu Now it's possible to keep playing your text while voca is in the background.
Wasabi Wallet v2.6.0 nostr:npub1jw7scmeuewhywwytqxkxec9jcqf3znw2fsyddcn3948lw9q950ps9y35fg
- Support for Standard BIP 158 Block Filters
- Full Node Integration Rework
- Create & Recover SLIP 39 Shares
- Nostr Update Manager
Futr nostr nostr:npub18wxf0t5jsmcpy57ylzx595twskx8eyj382lj7wp9rtlhzdg5hnnqvt4xra
- Solved memory leak in Qt5
- Fixed recursive re-rendering bug in Qt5
- Enable QML debugger through Haskell binding
- Improve event handling and Qt5 signal triggering
ZEUS v0.11.0 nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5
ZEUS v0.11.0-alpha3 with Cashu support is now available for testing: * Fix: addresses issues with sweeping Cashu tokens to self-custody with remote connections * Feat: Core Lightning: Taproot address support * Misc: UX enhancements * Cashu wallets are tied to Embedded LND wallets. Enable under Settings > Ecash * Other wallet types can still sweep funds from Cashu tokens * ZEUS Pay now supports Cashu address types. You can switch between Zaplocker, Cashu, and NWC mode but can only use one at a time.
Oracolo nostr:npub10000003zmk89narqpczy4ff6rnuht2wu05na7kpnh3mak7z2tqzsv8vwqk
Now the short notes block has two new styles: "Board" and "Full content"; the former shows notes in a pinterest-like fashion on two columns, while the latter shows full notes in full screen.
Umbrel 1.4.1 nostr:npub1aghreq2dpz3h3799hrawev5gf5zc2kt4ch9ykhp9utt0jd3gdu2qtlmhct
- Search files anywhere with ⌘/Ctrl + K
- New Favorites & Recents widgets
- Real-time transfer speed + ETA
- Snappier performance
- Several other enhancements & fixes
Shopstr v0.4.2 nostr:npub15dc33fyg3cpd9r58vlqge2hh8dy6hkkrjxkhluv2xpyfreqkmsesesyv6e
This update brings the following improvements and fixes: * Added Blossom media support for image uploads with metadata stripping * Added a terms of service and privacy policy * Added pagination for product viewing * Fixed relay list duplication bug * Removed excessive bottom margin on marketplace page
nostr.build nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7
The latest free features are: * 100MB upload size * Blossom support * David Lynch tribute page
openvibe nostr:npub1plstrz6dhu8q4fq0e4rjpxe2fxe5x87y2w6xpm70gh9qh5tt66kqkgkx8j
- Share Even Further : Crosspost from one network to another, or take posts beyond the open social web. Share anything, anywhere — effortlessly from
Ditto.13 nostr:npub10qdp2fc9ta6vraczxrcs8prqnv69fru2k6s2dj48gqjcylulmtjsg9arpj
Ditto 1.3 is all about discovery. From improved search and event fetching to a brand-new Explore tab, this release makes it easier than ever to find people, posts, and conversations across the #Nostr network. We've also rolled out streaks, media improvements, translation upgrades, and key admin tools.
Long-Form Content Eco
In the past two weeks, more than 356 long-form articles have been published, including over 90 articles on Bitcoin and more than 37 related to Nostr, accounting for 36% of the total content.
These articles about Nostr mainly explore the ongoing evolution and challenges of the decentralized protocol, including relay scalability, spam mitigation, signer tools, and publishing workflows. They highlight the network’s technical progress as it handles increasing data loads and infrastructure demands, while also addressing issues like spam and search limitations. Many articles focus on content creation and distribution, showcasing tools for decentralized publishing and media hosting. Others introduce practical guides for secure identity management and signer usage. The ecosystem’s economic potential is also discussed, with suggestions for monetization and community growth. Personal reflections and critiques further illustrate the culture and complexity of Nostr as it expands.
These articles about Bitcoin cover a broad spectrum of topics, highlighting its evolving role in technology, culture, and the global economy. They discuss core concepts such as decentralization, financial sovereignty, and Bitcoin as digital gold, while also addressing current issues like OP_RETURN restrictions, mining centralization, and environmental concerns. Real-world use cases—such as remittances, merchant adoption, and Bitcoin's growth in emerging markets like Africa and South America—are frequently explored. Many articles focus on user education, including wallet security, key management, and node operation. Others provide commentary through book reviews, political reflections, and personal narratives, illustrating how Bitcoin is shaping both individual behavior and institutional thinking.
Thank you, nostr:npub186a9aaqmyp436j0gkxl8yswhat2ampahxunpmfjv80qwyaglywhqswhd06 nostr:npub1xncam2l8u5chg6w096v89f2q2l0lz4jz4n7q7tdjsu6y5t9qea7q2cmrua nostr:npub10m6lrv2kaf08a8um0plhj5dj6yqlw7qxzeag6393z352zrs0e5nsr2tff3 nostr:npub15hhygatg5gmjyfkkguqn54f9r6k8m5m6ksyqffgjrf3uut982sqsffn4vc nostr:npub18ams6ewn5aj2n3wt2qawzglx9mr4nzksxhvrdc4gzrecw7n5tvjqctp424 nostr:npub1rsv7kx5avkmq74p85v878e9d5g3w626343xhyg76z5ctfc30kz7q9u4dke nostr:npub1jp3776ujdul56rfkkrv8rxxgrslqr07rz83xpmz3ndl74lg7ngys320eg2 nostr:npub1dk8z5f8pkrn2746xuhfk347a0g6fsxh20wk492fh9h8lkha2efxqgeq55a nostr:npub18sufer6dgm9gzvt8gw37x08dk8gxr8u80rh8f4rjv4m4u73wlalsygnz5q nostr:npub1qpdufhjpel94srm3ett2azgf49m9dp3n5nm2j0rt0l2mlmc3ux3qza082j nostr:npub1th6p84x9u5p4lagglkvm8zepa2dq4s9eanp57vcj4w5652kafads7m930q nostr:npub1xx8t4wk2cvnz5ez7sxkvx40phgqa05a8qas4mcss0fjcdx3x96hq7jdm20 npub1qn4ylq6s79tz4gwkphq8q4sltwurs6s36xsq2u8aw3qd5ggwzuf, nostr:npub1jrr9dlerex7tg8njvc88c60asxnf5dp8hgcerh0q8w3gdyurl48q6s5nwv nostr:npub1harur8s4wmwzgrugwdmrd9gcv6zzfkzfmp36xu4tel0ces7j2uas3gcqdy and others, for your work. Enriching Nostr’s long-form content ecosystem is crucial.Nostriches Global Meet Ups
Recently, several Nostr events have been hosted in different countries. * Recently, YakiHonne collaborated with the University of Jos and Ipaybtc community to successfully host two Nostr Workshops, attracting over 50 enthusiastic participants. The events not only provided a comprehensive introduction to the Nostr ecosystem and Bitcoin payments but also offered hands-on experiences with decentralized technologies through the YakiHonne platform.
The Nostr & Poker Night* was held on April 30 at the Bitcoin Embassy in El Salvador.The event featured an engaging Nostr-themed presentation by nostr:npub1dmnzphvk097ahcpecwfeml08xw8sg2cj4vux55m5xalqtzz9t78q6k3kv6 followed by a relaxed and enjoyable poker night. Notably, 25% of the poker tournament prize was donated to support MyFirstBitcoin and its mission to provide Bitcoin education. * A free webinar on venture capital, Bitcoin, and cryptocurrencies was held online on May 6 at 12:00 PM (ARG time). Organized in collaboration with Draper Cygnus, the event introduced the fundamentals of venture capital, showcased the projects of ONG Bitcoin Argentina Academy, and provided attendees with the opportunity to interact with the guest speakers. * Bitcoin Unveiled: Demystifying Freedom Money was held on May 10, 2025, at Almara Hub. The event explored Bitcoin’s transformative potential, helping participants understand its purpose, learn how to get started, build a career in the Bitcoin space, and begin their Bitcoin savings journey. Featured speakers included nostr:npub1sn0q3zptdcm8qh8ktyhwtrnr9htwpykav8qnryhusr9mcr9ustxqe4tr2x Theophilus Isah, nostr:npub1s7xkezkzlfvya6ce6cuhzwswtxqm787pwddk2395pt9va4ulzjjszuz67p and Megasley.
Here is the upcoming Nostr event that you might want to check out. * The Bitcoin 2025 conference was held from May 26 to 29 at the Venetian Convention Center in Las Vegas, with the Nostr community hosting a series of vibrant activities. While the Nostr Lounge served as a central hub for socializing and technical exchange, featuring app demos, lightning talks, and limited-edition merchandise. Nostr also delivered two key presentations during the conference, focusing on multisig key management and the future of decentralized social media. * BTC Prague 2025 is the largest and most influential Bitcoin-only conference in Europe. It will take place from June 19 to 21, 2025, at PVA Expo Praha in Prague, Czech Republic. The event is expected to attract over 10,000 attendees from around the world, including entrepreneurs, developers, investors, and educators.
The conference will feature more than 200 speakers from various sectors of the global Bitcoin ecosystem, nostr:npub14gm6rq7rkw56cd08aa4k5tvjnepqnxm4xvc535wj0wyjxlgrfa8sqdgv87 nostr:npub1dg6es53r3hys9tk3n7aldgz4lx4ly8qu4zg468zwyl6smuhjjrvsnhsguz nostr:npub1ymgefd46k55yfwph8tdlxur573puastaqdmxff4vj20xj0uh3p2s06k8d5 nostr:npub1jt97tpsul3fp8hvf7zn0vzzysmu9umcrel4hpgflg4vnsytyxwuqt8la9y nostr:npub1dtgg8yk3h23ldlm6jsy79tz723p4sun9mz62tqwxqe7c363szkzqm8up6m nostr:npub1g53mukxnjkcmr94fhryzkqutdz2ukq4ks0gvy5af25rgmwsl4ngq43drvk nostr:npub16c0nh3dnadzqpm76uctf5hqhe2lny344zsmpm6feee9p5rdxaa9q586nvr
and more. In addition to the main program, several side events will be held, such as Developer Hack Days, Cypherpunk gatherings, and Women in Bitcoin initiatives.
Additionally, We warmly invite event organizers who have held recent activities to reach out to us so we can work together to promote the prosperity and development of the Nostr ecosystem.
Thanks for reading! If there’s anything I missed, feel free to reach out and help improve the completeness and accuracy of my coverage.
-
 @ fd78c37f:a0ec0833
2025-05-13 07:37:28
@ fd78c37f:a0ec0833
2025-05-13 07:37:28Author:塔林·克里斯滕森(Taryn Christiansen),DoraHacks
摘要:本文探讨了人工智能和自动化的未来。在考虑了关于人工智能和自动化是否有益的各种观点后,文章提出,如果工作(work)作为一项社会制度变得基本过时,就需要一种新的黑客范式,以提供“质性(qualitatively)丰富机会”,让人们能够行使其能动性(agency)。也就是说,由于工作在人类发展中起着根本性作用,需要其他机会来填补这一空缺。本文主张,开源生态系统(open source ecosystems)对于实现这一目标至关重要。文章接着认为,像谷歌和亚马逊这样的潜在AI垄断者,将缩小人们在瞬息万变的经济中找到有意义的工作的空间。
Part 1
自动化的浪潮无疑正在到来。人类劳动将迅速贬值。人工智能已经取得了巨大的进展,并且,随着许多创新降低了成本,越来越多的企业将能够整合这一技术。随着生产模式、资本和供应链越来越多地实现自动化,生产力和效率将加速发展。
问题是,这是否是好事。答案五花八门。从末世论者如埃利泽·尤德科夫斯基(Eliezer Yudkowsky)[1] 和罗曼·扬波尔斯基(Roman Yampolskiy)[2] 等人认为,人工智能有潜力——并最终将——消灭人类物种。人类将远远不如未来的人工智能高效,因此,当通用人工智能(AGI)得以实现时,智能机器很容易得出结论:人类消耗太多,世界没有人类会更好。然后是怀疑论者,如马克斯·泰格马克(Max Tegmark)[3],他认为应该暂停人工智能的发展,以便更好地将其与人类利益对齐。“只有当我们确信其影响将是积极的、其风险可控时,才应开发强大的人工智能系统[4]。 ”再者,也有技术乐观主义者,如马克·安德森(Mark Andreessen)[5]、萨姆·奥特曼(Sam Altman)[6]和雷·库兹韦尔(Ray Kurzweil)[7],他们主张人工智能将带来物质上的丰盈乌托邦。发展应该加速,监管者应当退让,未来将带来经济增长、生产力提高和生活水平的惊人提升。
在这里很难做出具体的预测。不同立场的人常常以某种“不可避免性”的口气宣扬他们的观点。安德森是乐观主义最著名的主张者之一,他坚信由快速技术进步所带来的未来将是每一代人梦寐以求的那种未来。将会有具备无限同情心和耐心的人工智能导师,使教育更加普及和易获取;医疗行业将大幅提升,提供更好的预测并减少错误;机器人可以执行危险的工作,从而让人们追求自己的愿望。经济效益也将是巨大的。由于生产成本的降低,价格将更低,人们的钱将有更强的购买力,需求将增加,新的工作岗位将被创造,工资也将提高。他主张这一观点的主要论据是历史先例。每次有新技术革命到来时,社会总会从中获得净效益(net good)。十九世纪石油工业的形成之前,鲸鱼行业雇用了成千上万的工人。石油取代了这些工作,但也消除了依赖屠杀成千上万头鲸鱼来制造日常产品的需求。汽车威胁了许多行业,但当它成为普遍拥有的财产时,突然之间,需要更多的道路、桥梁和加油站来满足需求。虽然将会有自动化,人工智能将以良好的成果充斥世界,赋予经济前所未有的机会,让人们找到工作、积累财富,并利用人工智能所创造的价值。
然而,人工智能不同于以往的技术发展。人工智能是一种智能的进步和普及,而不仅仅是机械化的进步。库兹韦尔写道:“第一次工业革命扩展了我们身体的能力,第二次则扩展了我们思想的能力。”但是,一种新变量意味着结果的不同。人工智能能够学习、适应、生成、发现、反驳、怀疑、确认、设定目标,能够制定手段,也许有一天它会拥有意志并感知情感。它变得越来越具能动性(agentic)和自主性(autonomous),能够承担和完成通过它自身流程所生成的任务。如果它现在还没有具备能动性,那目标是让它达到这一点。仅仅基于先前经验得出的预测可能是一种范畴错误,容易导致误导和错误。当然,过去的技术形式与人工智能之间存在重叠,但它们之间有一个明确的区别,并且这种区别应该指导我们的预测。
另一方面,末世论者的观点并不具备很大的现实意义。那些通常潜藏在末世论者警告背后的“终结者”般的情景是不太可能发生的。尽管正如埃隆·马斯克(Elon Musk)[8]最近在《乔·罗根播客》(The Joe Rogan Podcast)上所言,如果嵌入了错误的目标,也许像“太空奥德赛(Space Odyssey)”系列作品中的HAL 9000那样的情景[9]是可能的。考虑到DeepSeek公司最近在降低计算成本方面的进展,该公司开发的AI模型已具有与美国最先进的模型竞争的水平,一场新的竞赛已经宣告开始,事情将会加速发展。美国副总统在人工智能行动峰会上的讲话清楚地表明了这一点。当前存在着一场争夺国际技术主导地位的竞争,这将塑造未来,发展速度的减缓等同于举白旗。因此,如果对安德森的主张有任何可行的反对意见,那也必须集中在如何引导技术发展,而非停止它。这应当为关于自动化的讨论提供启示:如何最好地引导自动化以避免不良结果?我们需要一种积极主动的方式。
Section 1.1
安德森对自动化的乐观态度存在一个问题,那就是他过于确定新工作机会会得到足够的分配,供人们享受并加以利用。问题在于,经济正变得越来越依赖知识和信息。知识和信息的比重远远超过了体力劳动,而在市场上能够取得成功的人是那些拥有相关技能的人,这些技能需要通过教育和培训来获得。正如托马斯·皮凯蒂(Thomas Piketty)[10]在其《21世纪资本论》(Capital in the Twenty-First Century)一书中所观察到的,这是一个普遍的经济趋势,“趋同(即减少和限制不平等)的主要动力是知识的传播和对培训与技能的投资。”因此,随着经济日益依赖知识,那些没有相关技能或安全保障的失业工人将处于严重的不利地位。而那些拥有相关知识、技能和信息的人则更有优势,能够投资资本并增加财富。例如,即便经济增长和生产成本降低,那些没有技能的人将看到工资停滞不前。但是,假设由于生产成本降低,消费者的购买力增强,需求可能会上升,如果供应无法迅速满足这一需求,价格可能会随之上涨,从而引发需求拉动型通货膨胀。关键在于,经济和生产力增长可能无法自然应对的变量和情境。正如皮凯蒂所说,“没有自然、自发的过程能够防止不稳定、不平等的力量永久占据主导地位。”因此,必须采取积极的应对策略,来避开那些可能会导致漂浮在经济表面上的大量船只沉没的尖锐岩石。
在杰里米·里夫金(Jeremy Rifkin)[11]的《工作的终结》(The End of Work)一书中,他采用了更加严峻的语气:“(下一个)工业革命正迫使全球经济面临空前的危机,数百万人因技术创新失业,全球购买力急剧下降。”而埃里克·布林约尔松(Erik Brynjolfsson)[12]和安德鲁·麦卡菲(Andre McAfee)[13]在《第二次机器时代》(The Second Machine Age)[14]一书中提供了充分的理由,认为里夫金的观点具有一定的道理。他们认为,经济增长所带来的回报(bounty)——即通过较少的投入产生更多的产出,使商品更加便宜、更加易得,从而改善人们生活——并没有通过财富、收入和资本的分配,使每个人都被惠及而受益。换句话说,“科技进步的浪潮可能并不会使所有船只都得以提升。”例如,在上文提到的技能差距上,“自1970年代中期以来,拥有研究生学位的人的工资上涨了约25%,而高中辍学者的平均工资则下降了30%。”尽管自20世纪中期以来,美国GDP和经济生产力呈现“令人印象深刻的轨迹”,但该国的中位数收入却在下降,表明少数人正在获得好处,而大多数人却错失了机会:自里根时代以来,贫富差距不断扩大。布鲁金斯学会的这篇文章[15]也支持这一观点。
然而,也许这些观点的实际含义被错误的同情心所误导。尽管不平等的确存在,但这并不意味着它应该被视为最主要的关注变量。再次强调,技术创新使商品变得异常便宜,使人们的生活更加轻松、生活水平更高,并且通过提供更多商品、服务、信息和知识的可获取性,来满足人们的需求和愿望,从而让日常生活更便利。尽管财富分配可能存在不平等,但其整体增长使每个人都变得更好。而且,随着财富的进一步增长,这一趋势将持续。曾经只有富人能够负担得起的东西,如今大多数人都可以买得起。比如iPhone,它能提供比所有现存图书馆更多的信息,而历史上,只有最富有的人才能使用后者,而几乎任何人都能购买前者。欧洲最大的图书馆是1481年的梵蒂冈图书馆,馆内估计有三千五百本书籍和文献。ChatGPT估计,如果将网上的信息转化为书籍大小的量,将约合467千万亿本书。看看农业的发展。当经济学家米尔顿·弗里德曼(Milton Friedman)在1980年写《选择的自由》(Free to Choose)时,他写道,在《独立宣言》被签署的时代,“每20个工人中就需要有19个(从事农业劳动),以养活这个国家的居民,以及提供生产盈余以供出口,来交换外国商品。如今,只需要每20个工人中的不到1个工人,就能养活2.2亿美国居民,并提供生产盈余使美国成为世界上最大的食品出口国。”
彼得·蒂尔(Peter Theil)[16]常常宣称,问题是技术创新停滞,而不是与福利项目或分配模式相关的道德失败。科学和技术需要突破,以转变行业并提高生活标准。人工智能的智能革命,理应能够实现这一潜力。因此,也许最好是直接放手不管。专注于特定分配模式的公平或正义,就像尼采所说的那样,是一种“坏良心(bad-conscience)”——以被认为的集体利益为代价而追求个人利益时所体验到的罪疚感,但实际上,这种感受只会阻碍进步,而非推动它。真正和最好的目标,可以说是努力创新并创造推动历史发展的价值,这就像亚当·斯密(Adam Smith)[17]的“看不见的手”的隐喻一样,自然地调和了人们的自利。正如米尔顿·弗里德曼所说,“对于促使个人之间合作,进而使得每个个人都可以从合作中受益的状态而言,没有外部力量是必要的,没有对自由的侵犯是必要的。这就是为什么正如亚当·斯密所说的,‘只关心自身利益’的个人会‘被一只隐形之手引导,以推动一种与他的意图无关的目标’。”
Section 1.2
关于经济增长是否足以改善长期的福祉和生活水平的问题,存在着高度争议。这个问题显然在这里无法解决。然而,提到这一点的目的是为了表明两种观点都具有正确性。个人在市场上追求自己的利益,像价格和工资这样的变量通过人们的自愿交换达成平衡,已经带来了巨大的成果。但差距也随之产生。 自动化是一个潜在的威胁。忽视它并声称它是危言耸听是一个错误。在可能的人工智能颠覆之后,某种形式的平衡达成之前,过渡期可能是复杂的,并且可能造成不必要的痛苦,如果事先处理,这些痛苦本可以避免。革命性的新技术可能既有好的一面,也有坏的一面。例如,十五世纪的印刷术使人们摆脱了教会强加的信息控制,催生了科学文献涌现的浪潮,为文明提供了巨大的价值。但它也导致了激烈而血腥的宗教战争,因为它允许人们传播各种信息。因此,为了避免类似的结果,在实施任何能够重新安排和重组社会经济安排的技术时,采取主动的方式非常重要。
从这里出发,通常的推论是,监管措施是应对这些可能性最好的手段。但与其满足于监管,正如马克·安德森在拜登政府执政期间警告的那样,监管会导致人工智能垄断,本文将力图支持自由市场中的自愿交换,同时促进必要的社会合作,帮助人们适应并在一个越来越不依赖于人力资本的经济中发挥作用。
本文的担忧是人们失去行使自身能动性(agency)的机会,从而无法拥有对自己的生活的控制(control)感和影响(influence)感。如果大量的人失去参与工作的机会,将会出现一条鸿沟,阻挡人们在世界中通常实现自己潜力的方式。他们将不再有机会在关键的社会领域做出具有深远影响的生活选择,这些选择需要谨慎和远见。人们将失去测试自我、发现天性的倾向和兴趣、辨认自己重视的事物以及行使选择去追求它的机会。社会中培养毅力、动机和个人意志的主要机会将会丧失。如果工作将主要被自动化替代,那么需要一个新的机会媒介来取而代之。作为社会制度的工作需要进步,并保持人们成长和发展的途径。
20世纪的自由主义哲学家约翰·杜威(John Dewey)写道:“正如感觉需要可感知的对象来刺激它们,我们的观察、回忆和想象能力也不是自发工作的,而是由当前社会活动所设定的需求激发。”像教育和工作这样的社会环境提供了刺激特定能力和功能所需的活动媒介,这些能力和功能需要完成定义活动的任务。人们常常争论说,自动化将使人们摆脱繁琐和机械的工作束缚。他们将有更多时间寻找新的方式来表达自己的需求,并最终实现工作一直阻碍他们实现的目标。人们将有自由去实现自己的潜力。但这一切不会自发发生。需要有能激发实现真正自由、意义和目的的活动的环境。当一个人完全孤单地待在一个没有人阻碍其动作和倾向的房间里时,可以说他是自由的。这样的人可以随心所欲。但由于没有能够激发适当反应的情境,且没有成功与失败的可能性,也缺少需要合作和协调的场景,这些场景有助于培养社会和情感的能力,也没有必要发挥智力和解决问题的能力,这个房间里的人的成长会停止,反而会枯萎,无法实现自由。一个从天空自由下落、不被任何东西阻挡的人,他看似自由,其实并不自由,因为他注定会撞向地面。
正如弗朗茨·卡夫卡(Franz Kafka)所写:“我自由了,因此我迷失。”哲学家让-保罗·萨特(Jean-Paul Sartre)则说:“人类被注定要自由。”
因此,当前的问题是,如何开辟一个人们能够自愿进入其中,并找到表达美好生活所需能力的机会的空间。此类机会,旨在行使人们的能动性,将被称为“质性丰富(qualitatively rich)机会”,而能够实现这些机会的环境则被称为“质性丰富环境”。
一个体现“质性丰富机会”的“质性丰富环境”是“开源生态系统”(open source ecosystems),它应当是人工智能发展的主要模式,它提供了以下框架:市场将为人们提供机会,让他们通过具有挑战性和刺激性的工作来行使自己的能动性,进而实现有意义的项目。人们将不得不学习新技能,克服障碍,但这一过程不仅是为了保持一个人们可以竞争、做出选择、发展能动性的市场,同时也促进人们生活中的目的和意义。如果经济要关上旧有工作形式的门,比如流水线和服务性工作,那么应该为人们提供更多有意义的工作机会。正如经济学家泰勒·科文(Tyler Cowen)在《莱克斯·弗莱德曼博客》(Lex Fridman podcast)中指出的那样,人们需要事情做。他们不想只是待在家里,正如COVID封锁所证明的那样。如果例行劳动和低技术劳动将被自动化,那么唯一的选择是确保存在“质性丰富机会”,以便人们能够利用并行使自己的能力,进行有意义的工作。
因此,应该在经济中引入一种新的范式。从佩卡·希曼宁(Pekka Himanen)[18]的《黑客伦理》(The Hacker Ethic)一书中汲取灵感,人们应当从以工业为基础的工作范式转向一种“黑客范式”。在工业范式中,个体主要执行重复性的劳动任务,其目的仅仅是为了获取收入以维持生存。而黑客范式则以内在价值为核心,强调工作本身的趣味性、刺激性、创造性与游戏性,其特征是激情与游戏,而非“履行对工作的责任”或“为经济做出贡献”的社会义务,正如马克斯·韦伯(Max Weber)[19]在《新教伦理与资本主义精神》(Capitalism and The Protestant Ethic)中所揭示的那样。黑客范式强调人类能动性及其实现价值的潜力,这种价值能提升人类。工业范式则在工人与他们与世界的积极参与之间产生疏离感:工人对他们所贡献的工作漠不关心;人们通常不喜欢甚至讨厌他们的工作。他们在那里是为了赚钱,而不是参与有意义的工作。正如希曼宁所写:“改革工作形式不仅是尊重工人的问题,更是尊重人类作为人类的问题。黑客不认同‘时间就是金钱’的格言,而认同‘这是我的生活’的格言。”正如埃里克·史蒂文·雷蒙德(Eric Steven Raymond)在《如何成为黑客》(How To Become A Hacker)[20]中所说,黑客认为世界充满了奇妙的问题,并在致力于解决这些问题中找到了自由。他们寻找需要动机和热情的项目,并相信当其他人也有机会获得同样的自由时,世界将变得无限美好,这需要社会合作以及对信息的最大程度的开放获取——这也正是“开源”的重要意义所在。
为了凸显为何引入新范式对于应对人工智能的挑战至关重要,具有显著的历史意义,我们可以回到亚当·斯密的思想。随后,将进一步阐明“质性丰富环境”与“质性丰富机会”的概念,并将其应用于当下以专有技术(proprietary technology)为核心的人工智能垄断体系。届时可以看到,这些垄断将扼杀黑客范式的生成,因此是不可取的。
透过亚当·斯密的视角我们可以看到,尽管工业化在长期内极大地提升了人们的生活水平,但它也对从事重复性、机械性劳动的人产生了消极影响,因为这类劳动削弱了对人类认知能力的刺激,阻碍了其全面发展。劳动分工极大地加速了专业化的进程,却减少了个体接触那些能调动其高级心智能力的机会——而这些能力正是实现有意义、有目标、富有成就感的工作的基础。人工智能与自动化正成为一种转型催化剂,逐步替代工业时代的工作模式与生产逻辑,将人力资本曾承担的任务转交予智能机器完成。若人工智能真的是一种进步——即人类进步——那么它就应回应亚当·斯密关于劳动分工及其对人类生活影响的担忧。
Part 2
Section 2.1
亚当·斯密在1776年写下了《国富论》(The Wealth of Nations)。受到艾萨克·牛顿(Isaac Newton)的影响,斯密希望理解社会背后的设计,以及社会的运作机制,类似于牛顿发现并使用采用机械论术语来公式化了解释宇宙的物理法则。那个时代的模型是将现象看作是像精密调校的手表一样有组织和有秩序的,所有部件和机械都在完美的和谐中协同工作,产生各种各样的效应和涌现现象。
在斯密生活的时代,第一次工业革命正在英格兰进行。城市扩张,曾经仅限于富人阶层的商品和服务变得更加廉价且易于获取,生活水平提高,基础设施得到了发展,表面上看,人们过上了前所未有的更好生活。斯密观察到社会的进步。由于大发现时代以及使欧洲人能够踏上新大陆的技术,欧洲人与那些似乎尚未经历欧洲所经历的历史进程、被欧洲人认为是“未开化”的民族接触,因此,欧洲大陆的风尚(ethos)是历史和文明正在进入一个新的、更为先进的阶段。科学探索和知识带来的创新提升了生产力和效率,从而使社会系统的组织更加复杂。斯密希望了解推动这一进程的因果机制。
斯密观察并认为劳动分工在社会经济中扮演了主要的,甚至是基础性的角色。随着社会组织的扩展,制造与生产过程逐渐细分为更为专业的任务,结果这些过程的产出大幅增加。在传统的行会框架中,工匠将一生投入到完整的手工业中,学习所需的所有方面并精通每一部分。这种行会框架逐渐被分工化的工厂模式所取代,后者在日益发展的城市中通过劳动分工的方式系统化生产。一个庞大的个体系统因此浮现,它需要极高的协调性,而劳动分工则将这一系统组织成一个复杂的机制,旨在调和人们的利益。
斯密还认为,劳动分工反映了人类本性中的某些更深层次的特征。人们涌向城市,赚取劳动报酬并享受更好的生活条件,因为斯密认为,人类天生具有进行交换(truck)、易货交易(barter)和贸易(exchange)[21]的倾向。他写道:“交换、易货和将一种物品与另一种物品贸易的倾向是所有人类共有的,在其他任何动物种群中都无法找到。”像狼这样的动物自然地在等级化的群体中组织自己,刚孵化的小鸟倾向于飞行,而像树木这样的有机体则在密林中争夺阳光。与此不同,人类进行交换、易货和贸易,是因为他们有天生的倾向来改善自身状况。劳动分工推动了这一目标的实现。
然而,斯密认为,劳动分工是一种权衡——它也有代价。尽管人们的生活水平提高,他们享受更好的条件,能够满足诸如食物、水和住所等消费需求,但劳动分工却将工人简化为机器中的齿轮。这些任务几乎不需要认知努力。一旦任务变得常规化,并转化为肌肉记忆后,便没有更多的障碍或问题需要克服。因此,斯密深切担忧这一过程将随着时间推移产生深远的负面认知效应。人们去上班,只要他们熟悉自己的任务,就不需要动脑;他们机械地行动。斯密直言不讳地写道:
一个人一生都在执行少量简单的操作,并且这些操作的效果始终显而易见,他便无需发挥理解力,或利用自己的创造力去寻求解决从未出现的困难的方法。他自然会变得愚笨无知,几乎达到人类可能变得最愚笨和无知的地步。
劳动分工提供的机会在质性上较为贫乏,无法使人们具备过上有意义和有目的生活的能力。借用另一位启蒙时期哲学家伊曼纽尔·康德(Immanuel Kant)的术语,劳动分工未能尊重人类的尊严,而尊严要求针对并培养那些能够使人过上自主选择生活所必需的能力。拥有尊严意味着对个人生活拥有影响力(influence)和掌控力(efficacy)。
劳动分工创造了更多提高生活水平的机会,但它没有提供“质性丰富机会”,使人们能够整合他们的能力并实现全面的人生。大多数人可用的机会并未促使他们将创造性和生产力能力集中于那些能够扩展他们在世界中自由感的目标上。与行会制度相比,劳动分工提供了更多的机会,但这些机会也更浅薄,更缺乏产生掌控感的体验。但由于生活水平较高,人们正确地选择了将自己降级为齿轮的工作。但正如斯密所观察到的,提高生活水平不足以满足人类需求的全面范围。它没有让大多数个体能够发挥他们的更高能力。
斯密认为,必须进行改善。对人们而言,更多“质性丰富机会”是至关重要的,这些机会使他们能够过上更有意义和目的的生活,体现人类尊严,并为行使他们的能动性提供基础。劳动分工提供了物质自由的增益,但并未提供足够的机会以实现更内在的、主体驱动的自由。
这无疑是卡尔·马克思对资本主义的重大批评之一。在资本主义体制下,人们与他们的劳动发生异化(alienation)。劳动的异化意味着人们与自己的活动脱离;即人在其自身和它的创造与生产能力之间产生了距离。在心理学家埃里克·弗洛姆(Eric Fromm)关于马克思的著作[22]中,他写道:
对马克思而言,异化的过程表现在工作和劳动分工中。工作是人类与自然之间的积极联系,是创造新世界的过程,包括创造人类自身……但随着私有制和劳动分工的发展,劳动失去了作为人类力量表达的特性;劳动及其产品变成了与人类、与他的意志和计划分离的存在。
人类通过他们所参与的活动以及在其中投入的内在力量和驱动力来理解和塑造自己的身份。通过创造和塑造世界及其环境,并将能量集中于外部项目和目标,一个人在世界中实现自我感。活动(Activity),而非被动的消费或任务,定义了马克思所说的人类本质。正如弗洛姆在其著作《拥有与存在》(To Have or To Be)中所指出的,通过“存在(being)”,而非“拥有(having)”,一个人才能体验到生活的意义和目的。通过“在爱中存在”,“以充满激情的方式存在”,“以积极行动的方式存在”,“以有希望的方式存在”,“有目的地存在”,以及“以有生产力地方式存在”,一个人才能过上充实的生活,而不必依赖“拥有”(爱、激情、积极性,等等)这些东西。劳动分工强调“拥有”,而其所涉及的许多工作和活动并未促使人们发展出“存在感”。正如德国诗人歌德(Johann Wolfgang von Goethe)所言,人类通过“将自己从可能性的黑夜转化为现实的白昼”来努力存在。人类通过外化他们内心的价值观和设想来追求成为自我,而这一过程通过活动得以实现。弗洛姆写道:“人类只有在生产性行为中才是活着的,只有在他通过表达自己特定的人类能力来把握外部世界,并且以这些能力来把握世界时……在这个生产性过程中,人类实现了自己的本质。”劳动分工减少了人类的能动性感,即人类以他们所珍视的、选择并在其上实践自身意志的有意义的方式,来主动影响和引导自己生活的能力。
通过创建“质性丰富环境”,黑客范式及其对开源的推动提供了多个“质性丰富机会”,从而推动了我们社会和政治结构的进步。它具有实现人类天性中更为积极的一面——人的能动感——的潜力,而不仅仅是其消极和消费的部分。这里的主要假设是,如果人工智能要发展并融入经济基础,它应当使人们的生活得到改善。更具体地说,如果自动化发生,其结果应当是改善人们的生活,而非对他们造成伤害。实现这一目标的一种途径是确保足够分配“质性丰富机会”,让每个人都能从中受益,而开源正是实现这一目标的途径。人工智能发展可能导致人们境况恶化以及抑制他们潜在机会的一个重要原因是存在使用专有模型来控制人工智能并主导其市场使用的垄断现象。黑客范式和开源则为避免这种结果提供了可能的解决方案。
Section 2.2
在理解垄断如何减少“质性丰富机会”之前,我们需要进一步弄清楚什么是“质性丰富机会”,以及它们激发并帮助发展哪些能力。在解释这类机会的性质及其意义之后,我们将探讨垄断是如何大幅削弱这些机会的可及性,以及这意味着什么。
“质性丰富机会”的理念源自亚里士多德(Aristotle)[23],更具体地说,是由哲学家玛莎·努斯鲍姆(Martha Nussbaum)和经济学家阿玛蒂亚·森(Amartya Sen)进一步发展的。亚里士多德认为,人类要实现繁荣、过上充实而有尊严的生活,必须达成某些特定的功能(functions)或方式。他认为存在一种“人性(human nature)”,而这种人性包含基本的和更高层次的需求。无论历史和偶然条件如何变化,人类都具有一些根本特征。当然,这些特征是在历史情境中体现的,但在所有文化和文明中都可以观察到某些本质上的一致性。亚里士多德说:“善是万物所追求的目标。”所谓“善”,即是一种事物的适当功能。例如,眼睛的善是“看见”,种子的善是“长成一棵树”。实现某物的适当功能,就是实现其“繁荣”(flourish),也就是达到它所追求和努力趋向的状态。达到这样的状态,就是获得一种内在价值。
作为一个人去实现其功能,需要基本的生活必需品,如食物、水、住所和行动能力。但这些物品本身并不具有内在价值;它们之所以有价值,是因为它们使人能够运作以追求更进一步、更有内在价值的事物。如果一个人仅仅拥有这些基本的生存条件,我们可以说他“运作”着,但未必是“良好地运作”。要使一个人“良好地运作”,必须拥有其他内在价值更高的资源。人类需要教育与信息获取,以发展其认知能力;需要家庭和亲密关系,以发展社交技巧、个人身份认同和情感处理能力;还需要能够施展意志、探索兴趣、投入热情的追求,并培养目标感的渠道。一个良好的政治与社会安排,即我们应当追求的那种社会制度,应当为人们提供具体的机会,让他们得以实践这些需求,从而实现良好的人类运作状态。“质性丰富机会”即是指那些能够为人类发展内在有价值的能力(如做出知情决策的能力、制定值得追求的目标及其实现路径的能力,以及建立有意义、有影响力的人际关系的能力)提供基础的机会。像工作、教育、社区和艺术等社会制度,正是那些激发并促进实现这些目标所需能力的质性丰富环境。
质性丰富机会之所以重要,是因为它们使人们具备发展“能动性”的能力。借用斯坦福大学心理学家阿尔伯特·班杜拉(Albert Bandura)[24]的概念,我们可以将“人类的能动性”理解为个体感受到自己对生活有控制和影响力的能力。更具体地说,质性丰富机会能够激发那些针对“自我效能”(self-efficacy)能力的行为。所谓“自我效能”,是指一个人在面对挑战和障碍时所拥有的自我信心感。当面对一个困难且新颖的任务时,高自我效能的人会评估自己有能力克服困难完成任务;他们会拥有坚持不懈、克服失败的动机;即使身处陌生与复杂情境中,他们也能维持良好的心理状态。质性丰富机会旨在发展那些能够提升自我效能以及应对具体情境所需的能力。通过这些机会,一个人得以锻炼其能动性、获取掌控力,从而扩展其自由感。而正如班杜拉(1994)[25]所说:“一个人自我效能感越强,他为自己设定的目标挑战越高,并且对这些目标的承诺也越坚定。”因此,通过增强自我效能,无论是在信念层面还是实践层面,个人将获得更高程度的自由,并过上更具质感、更丰富的人生。
工作在塑造个体身份和自我认同方面具有至关重要的作用。它为人们提供了探索不同职业路径的机会,使他们能够发现自己在人生中希望追求的目标。工作往往也是建立职业与个人关系、融入不同社会网络的重要方式,同时也是人们获取能力、攀登社会阶梯的媒介。工作这一领域还能帮助人们在多种环境和情境中培养动机、智力以及态度。换句话说,工作为人们提供了发展某些功能或生活方式的机会,而这些功能和生活方式正是实现美好生活所必不可少的。
例如,想象一个年轻人第一次进入劳动力市场。他尝试了几份工作。他发现自己不太喜欢零售业,因为需要持续与顾客打交道。他又尝试了送货服务,结果发现自己不喜欢那种日复一日的重复性工作。最后,他在一个建筑工地找到了工作,并发现有些任务既有趣又具有挑战性。他喜欢动手工作的感觉,于是决定投身技工行业。这个人随后进入技校学习,建立起重要的人际关系,在新环境中受到挑战,被激发去提升技能、积累知识与经验,并在这个过程中不断面对和克服新的困难与障碍。毕业后,他抓住了一个机会——一位欣赏他职业精神的导师为他提供了许多关注和支持。之后,他在某家公司工作了一段时间,并在这个过程中积累了足够的知识和自信,决定创办自己的公司,以实现这个目标。他开始建立客户关系,专注于能让自己在竞争中脱颖而出的技能,并最终打造出一家成功的企业。
这听起来也许有些理想化,但却是一个既熟悉又现实的例子。它描绘了一种有目的的生活,这些目的是通过在环境和情境中发现的机会而形成的,这些环境和情境提供了能够产生能动感和自我价值感的体验。当然,要实现这样的人生画面,通常还需要一系列其他条件,例如成长于一个有支持的环境中,拥有探索个人兴趣所需的资源和时间等——但在美国,工作无疑是提供发展构成美好生活的关键功能的核心渠道。上文中的这个人通过学习新技能、克服挑战、做出关键选择来应对社会环境,最终实现了成功与成就。随着在专业领域的成长,他不断设立新的目标,并获得足够的自我效能感,相信自己能够实现这些目标。他发展出一整套完整的能力体系,最终也获得了尊严感。无论这个人过去或未来是否还拥有其他美好的人生经历,如果没有那些能够让他工作与成长的机会,他的人生质量将会大打折扣。
这里有一个真实的例子,不过这个人将保持匿名。在荷兰大学毕业后,他不想找一份“普通的工作”,于是开始前往其他国家旅行。他靠在 YouTube 上制作音乐赚了一些钱,住在各地的酒店和青年旅舍。但随着资金逐渐减少,孤独与疏离感开始加剧,他变得抑郁。他完全自由——可以去任何地方、看任何东西,做任何他想做的事——但他感到极度孤独。在亚洲的一家青年旅舍,他一个人躺在床上盯着天花板,没有钱、没有女朋友、也没有工作,他想起了父亲曾对他说的话:“他小时候教过我:每当我感到沮丧或者不知道做什么时,就去找一座沙堆,拿把铲子,把沙子从院子的一边搬到另一边……干点体力活,做点辛苦的事——做点什么。我做创业项目时也一样。”于是,他开始学习编程,开发软件和应用程序,并利用 Stripe 平台[26]将作品发布给公众以筹集资金。他专注于那些能够带来方向感与创作机会的活动。在真正的“黑客精神”指引下,他把世界看作充满待解决问题的迷人场域,有些问题他认为是可处理且值得去做的,于是尝试去解决。令人惊讶的是,他立下目标:一年内创办十二个初创公司——而他真的做到了。
这个人起初感到疏离与孤独,缺乏人生目标。因此他选择行动起来,把自己投入到使用基础编程语言与工具进行的创造性表达中。通过利用人工智能,他也更能创造出具有价值和实用性的产品,供他人使用与体验。他采纳了父亲的建议,将自己投入到实际行动中,结果是抑郁与焦虑逐渐缓解。他在信息丰富的环境中,发现了许多“质性丰富机会”,得以发展自我,提升自我效能感与能力。他与更多富有挑战性的目标建立联系,不断努力达成这些目标。而开源技术在这一过程中扮演了关键角色。
这也正是 Dora 生态系统的重要意义所在。通过像 DoraHacks.io 这样的平台,像上文所描述的那样的人们可以借由“质性丰富机会”,与全球各地的开发者协作,共同创新,创造出人们认为紧迫且相关的有意义的解决方案。该生态系统为开发者提供了必要的资源,使他们能够加入全球任何地方的 “BUIDL” 团队,解决引人入胜的问题;并在黑客松中与其他建设者一起感受到社区归属感;同时还通过激励机制推动他们实现有意义的目标,而这些目标往往又会引发更具挑战性和刺激性的下一阶段任务。Dora 生态系统创造了一个充满可能性的环境,使人们能够构建去中心化的产品与服务,例如将所有权交还给用户本人,增强他们在数字世界中的自主性、安全性以及对金融资产的控制力。正如下文将进一步讨论的,大型企业和垄断机构通常并不会从这些类型的技术中直接受益。那么,他们又有什么动机去资助这类技术呢?开源技术栈能够提升价值的质量,因为它为人们提供了开发更具意义产品的路径,而这些产品通常比那些由大型、目标狭隘的机构所产出的产品更具意义。
因此,如果自动化有可能减少甚至消除人们运用能动性、获得自我效能感的“质性丰富机会“,那么它所腾出的空间,理应由其他在质性上更丰富的机会来填补。如果确实存在“人性”这样的东西,而这种人性包含了一系列需要被发展、以使人得以过上有尊严生活的能力,那么最优与最值得追求的政治与社会安排,应当是将“质性丰富机会”公平分配,以确保人们有选择去运用自身能力、成为能够良好运作并实现繁荣生活的个体。为人们提供质性丰富机会,使他们能够加以利用,并据此组织、调动并集中自身内在力量于那些能够锻炼与激发个体能力的实践之上,这就构成了一个让人过上更有意义人生的基础。它是给予人们成为他们所珍视之人的自由。
接下来的部分将转向对 AI 垄断企业的讨论,揭示它们是如何压制上述这类未来机会的。
Part 3
Section 3.1
人工智能领域中潜在的垄断者不言自明:谷歌、苹果、微软、Meta 和亚马逊。这些公司以及少数其他企业在 2024 年占据了 65% 的固定网络流量和 68% 的移动网络流量[27]。谷歌大约占据全球约 90% 的搜索市场,其品牌名几乎已成为“搜索”行为本身的代名词;Meta 拥有主要的社交媒体平台,如 Instagram、Facebook 和 WhatsApp,这些都是人们日常交流与信息分享中访问量极高的平台;微软控制着大约 72% 的桌面操作系统市场;在美国,苹果约占据 60% 的智能手机市场份额;而亚马逊则主导了线上零售,其规模“超过美国排名其后的 15 家最大电商零售商的总和”[28]。此外,谷歌、Meta 和亚马逊合计占据了美国约 60% 的广告收入。我们在网上所接触到的产品、精美广告、以及注意力的买卖,主要都是由这几家大型科技公司驱动的。根据 Synergy Research[29]的研究,到本世纪末,微软、谷歌和亚马逊三家公司可能将掌握全球高达三分之二的数据份额。这些公司还控制着大部分云基础设施——亚马逊、微软、谷歌(以及阿里巴巴)合计拥有全球 67% 的云计算市场份额[20]。
这些公司拥有庞大的资源储备,同时也长期以来采用各种手段排挤竞争对手,包括通过并购消灭潜在威胁、利用市场主导地位优先推广自家产品、实行掠夺性定价、利用网络效应,以及其他众所周知的策略。例如,鉴于亚马逊在电子商务领域的市场主导地位,它可以通过优先推荐自家产品,排挤其他可能品质更高的供应商产品。消费者在面对价格更低的亚马逊产品时,往往更倾向于购买,而亚马逊正好拥有充足的资源来维持这种低价策略。在网络效应方面,“目前[31]大多数科技巨头的用户数量都以十亿计”,这为初创企业和小公司制造了几乎无法跨越的障碍。而谷歌也多次被指控故意降低某些内容的排名,并优先展示有利于自身利益的信息。
如今,这些公司正积极争夺对人工智能发展的主导权。“Meta、微软、亚马逊和Alphabet 预计在2025年将累计投入高达 3250 亿美元的资本支出与投资……相比这些公司在2024年报告[32]的约 2230 亿美元,这相当于增长了 46%。”此外,“几乎没有例外,所有初创公司、新进入者,甚至 AI 研究实验室都依赖这些大型科技公司:他们依靠微软、亚马逊和谷歌的计算基础设施来训练系统,也依靠它们庞大的消费市场渠道来部署和销售 AI 产品[33]。”科技巨头垄断了初创公司赖以生存[34]的关键资源——人才、数据和算力。 现有的行业巨头正在开发各种模型,以维持其在各自市场中的立足点。由于它们掌握着大多数资源——例如,“这些公司贡献了标普500指数公司市值的 22% 以上,其单独市值甚至超过了加拿大、意大利等[35]部分 G7 国家 GDP”——它们可以随意挤压竞争对手,阻止初创企业和小型公司进入市场。正如前文所述,随着 DeepSeek 在全球市场中作为竞争者不断取得进展,这些最大规模的 AI 公司正在大肆渲染一场“军备竞赛”,并夸大中国威胁以及人工智能可能带来的危害,从而推动对 AI 的监管和开发限制,而这些限制最终最有可能使它们自身受益。与此同时,由于垄断体制依赖于专有模型,其架构、权重、学习算法、代码以及内嵌目标都对公众隐蔽不明,在 AI 渗透信息网络的过程中,这些公司的经济与市场主导地位也将以一种“隐秘的方式”塑造人们的思维和行为。
那么,监管是否能解决这个问题呢?《麻省理工科技评论》最近指出:“监管或许有帮助[36],但政府政策最终往往加固了这些公司的权力,而非加以削弱——这些公司能够利用其资本与政治影响力来操控政策。”亚历克斯·蓝姆佩尔(Alex Rampell)[37]最近写道[38]:“拜登政府发布了一项行政命令[39],试图以人为设定的门槛限制计算能力,禁止开源技术,理由是其对国家安全构成威胁,同时这实际上为几家最大公司垄断监管资源敞开了大门。”例如,尽管萨姆·奥特曼在与贝利·韦斯(Barry Weiss)[40]的《自由新闻播客》(Free Press podcast)中否认了这一说法,投资人马克·安德森却一再警告称,拜登的 AI 行政命令的真正目的在于将 AI 的控制权交到少数几家公司(极可能是 OpenAI)手中,并通过提高市场准入门槛来消除竞争者。此外,尽管此举颇具争议、甚至可能显得天真,自从 DeepSeek 发布其 V1 和 V3 模型以来,Anthropic的 CEO 达里·阿摩地(Dario Amodei)一直呼吁加强出口管制政策[41],进一步限制中国获取芯片的能力。然而,正如迪伦·潘特(Dylan Patel)[42]和纳森·兰伯特(Nathan Lambert)[43]在 《莱克斯·弗莱德曼博客》中指出的那样,DeepSeek 的开源模型显然并不构成任何实质性的国家安全威胁。但它确实对那些依赖专有系统、通过模型控制潜在价值的生态构成了威胁。DeepSeek 的方法迫使这些“专有资本”朝着可被任何人使用与构建的公共资源方向转化。正因如此,阿摩地对“单极 vs. 双极世界”的坚持背后其实包含着竞争性的动机:要么 AI 权力集中于美国,要么中美都拥有对等的 AI 能力——而后者,在阿摩地看来,是必须避免的局面。
或许,我们应当持有一种不那么鹰派的乐观态度。经济学家泰勒·科文提出了充分理由,认为与其全面投入一场军备竞赛,不如在相互合作[44]与共赢中寻找发展路径。当然,竞争仍然是必要的,但推动未来事件进程的竞争心态,不应仅仅源于达尔文式的“适者生存”逻辑,而应更接近尼采所观察到[45]的古希腊式“竞技”(Agon)[46]传统——那是一种社会制度,其中的艺术家、军事领袖与运动员通过竞争彼此激励、共同成长。
没有对手,竞争者也将迷失方向。因为没有了改进、突破和创新的机会,个体便失去了变得更好、更具创造力的可能。竞争者的存在本身就依赖于愿意对抗他们的人。正是因为有人挑战,希腊诗人才得以想象得更深远、表达得更出色。尼采指出,希腊竞技者面临的最大危险不是失败,而是——失去竞争对手。他写道:“这正是希腊竞技理念的核心:它厌恶独裁,畏惧其危险,它渴望用‘另一个天才’来抵御某一位天才的压倒性力量。”我们不应将竞争理解为自然状态下的求生挣扎,那种资源稀缺、人与人互为威胁的霍布斯(Thomas Hobbes)式处境——“孤独、贫穷、肮脏、残暴而短暂”[47]。我们也不应将竞争本能视为某种原始性冲动的残余,只为了压制对手、消灭威胁。我们应当将其理解为一种可以高贵化的本能,正如尼采所言,它是“所有人类情感、行为与作品的唯一丰沃土壤”。竞争本能自身也具有德性,应当被培养成“在正确的时间、以正确的方式、出于正确的理由”去发挥作用的东西(亚里士多德,《尼各马科伦理学》(Nicomachean Ethics)第二卷),而不是被视作一种必要之恶。阿摩地害怕中国,这可能不是正确的回应——或许,一个更好的、更具德性的回应,是将中国视为值得尊敬的竞争者。
Section 3.2
现在让我们聚焦于这些潜在的 AI 垄断企业为何会通过主导 AI 生态系统,压制质性丰富机会的更广泛传播。原因至少有两个:第一个涉及经济能动性,第二个涉及价值能动性。所谓经济能动性,是指人们进入市场、创造能满足消费者需求与欲望的价值与效用的能力。如果市场上的 AI 模型被集中掌握在少数公司手中,新兴企业与创业者为世界做出有价值贡献的机会将受到限制。那些能够回应民主、医疗保健、金融自主、政治权利与自由,或其他重大而有意义问题的创新,将大幅减少,从而也会降低 AI 所可能带来的社会福祉。任何威胁到这些少数 AI 垄断企业的控制力、影响力或财富的产品与服务,将被直接排除在市场之外,而不是由市场自然机制或消费者的真实需求所决定。
另一方面,所谓价值能动性,是指人们有能力对社会应追求的目标产生影响、发表意见。如果 AI 是在不透明的条件下、依据无法被公众了解和介入的价值与目标进行训练的,那么人们在这些问题上的影响力就会被削弱。如果由专有模型决定大多数或几乎全部嵌入 AI 的产品与服务的性质,那么人们对这些技术的控制权将大为减少。例如,所谓“对齐问题”指的是如何使 AI 与人类的利益保持一致。那么,什么是人类的利益?什么是构成一个良好且值得追求社会的目标?AI 的运行应遵循哪些道德与伦理原则?这些价值是否可以由少数几家公司决定,而无需公开其训练数据与学习算法?是否可以不接受公众监督与介入?如果技术架构被封闭在公众视野之外,那么上述问题的答案就更有可能来自权威的决定,而不是通过民主程序获得的共识。
经济能动性与价值能动性的双重丧失是危险的,本文余下部分将进一步阐述原因。
Section 3.3: 经济能动性
正如奥地利经济学家路德维希·冯·米塞斯(Ludwig von Mises)与弗里德里希·哈耶克(Friedrich Hayek)所著名指出的,苏联之所以在某些方面具有毁灭性,部分原因在于它无法通过自然发生的市场机制来合理分配资源。在这样的体制下,由内部的中央计划者来决定人民的需求与欲望——而这些人所掌握的信息资源既稀缺、又充满偏见与误差,无法实现准确分配。因此,大量官僚主义和强制性的手段被实施来调配国家资源。
举例来说,国家必须设定价格。至少是在苏联的情况中,并不存在一个广泛可用的自由市场,来使商品与服务受到供需关系的调节。生产者依据国家命令进行生产,而非根据市场激励(如竞争)自行调整方向——这些激励本应协调生产与消费,促成市场均衡。换句话说,价格失去了其关键信息功能——它本应指示资源该流向何处。哈耶克在《通往奴役之路》(The Road to Serfdom)中写道:“任何对某些商品的价格或数量的控制,都剥夺了竞争协调个体努力的能力,因为此时价格变动无法反映环境中的相关变化,也就无法为个体行动提供可靠的指导。”
不过,对本文来说,更重要的是:国家控制的生产与经济计划还意味着人们被剥夺了进入市场并创造价值的机会,使他们难以通过创新改善自身生活。任何可能威胁国家权力、削弱其合法性与影响力,或转移其部分控制权的创新行为,都将被禁止进入市场。举个例子:假设某人观察到,在某国的偏远乡村地区,由于常年洪水泛滥,人们无法修建道路,从而难以参与国家选举。这位发明者研发了一种不受洪水腐蚀的新型混凝土,并希望在乡村修建道路,改善人们的通行条件,让他们更容易参与公共事务。但当他向国家交通委员会申请资源时,却遭到了拒绝。原因是:该地区居民普遍希望拥有农业生产的自主权,因此国家不愿意为这些人提供进入选举制度的通道。而在缺乏市场竞争的情况下,也没有其他机会和机制可以去建设这些道路。
垄断,尤其是在受到监管体系保护的情况下,构成了类似的威胁。马克思曾做出一个著名批评:资本主义作为一种社会制度,其内在逻辑会逐步而不可避免地导致生产资料向少数人手中集中。虽然包括哈耶克和米塞斯在内的许多经济学家认为这种看法是错误的,并坚信在正常运作的资本主义体系中,这一结果是可以避免的。但如果人工智能遭到垄断,那么马克思的预测将比以往更加接近现实——无论这是由于历史规律,还是由于无法预见的结构性变数所致。正如克里斯·迪克森(Chris Dixon)[48]在其著作《阅读、写作、拥有》(Read, Write, Own)中观察到的,初创公司之所以能在市场中找到生存空间,部分原因在于大公司往往目光短浅,无法及时察觉到新兴产品正逐步获得消费者的关注。在专注于自身业务的过程中,这些巨头常常错失市场趋势与动向,而初创企业若运气足够好,就能积累足够势能以形成竞争力。但如果这些老牌巨头掌控了人工智能,他们就可能利用 AI 的能力来抹平初创企业原本可以利用的那些优势。随着时间推移,垄断企业将对市场形成难以穿透的控制权,各行各业的价值链最终将进一步“上游集中”到这些公司手中——比现在更甚。由专家所忽视、却能在市场中创造出意想不到价值的颠覆性技术,其创新空间可能会被完全挤压出去。
由于人工智能具备智能能力,它作为资本工具拥有极大的潜力,能够创造出改善人类生活的先进技术。但,由于有些对公众最有益的应用方式,可能并不符合政府与大型企业的利益,其潜在福祉也就可能在权力结构中被悲剧性地削弱。其中最明显的例子就是金融自主权。
看看比特币的案例就足以说明问题。中本聪(Satoshi)[49]发明比特币的初衷,是为了让人们拥有金融自由的能力——通过创造一种稀缺资源,其价值储存功能可与黄金相类比。比特币使那些生活在高通胀、货币极度贬值国家的人们,能够积累具有全球流通性的财富。人们可以拥有一种不会因货币供应过量或国家财政赤字上升而贬值的资产。比特币能够帮助人们过上更加稳定、安全的生活,它提供了透明性、个人所有权,以及能够激励社会合作的制度安排——这一切都无需依赖强制性信任或道德施舍。
人们本希望掌权者能够设法将中本聪为世界带来的巨大价值纳入现有体系。并不是说比特币应立即取代法定货币,而是说,考虑到比特币在应对法币体系中潜在致命问题方面提供了极具前景的解决方案,政府至少应当付出更大的努力,将这些解决方案纳入实践。合理的期待是,执政者会寻求一种方式,将区块链、比特币及其增强经济自由的潜力加以整合。然而,直到最近,有关这一技术的监管进展一直缓慢而混乱。在拜登政府期间,由于政策缺乏清晰性与明确性,关于加密货币的许多举措都未能充分发挥其潜在价值,反而阻碍了其更高效、更具生产性的使用路径。
如果AI被通过监管框架实现垄断,那么那些原本有潜力改善人类生活的技术也可能轻易被弃置。若这些技术与政府或企业利益发生冲突,大多数人将无法通过授权或专利使用这些专有模型,而中小型企业也会被并购吸收。尽管人工智能本可以彻底革新选举平台及人们参与选举的方式;尽管它本可以通过更优的数据安全手段或创造更多经济机会来增强个体自由,但探索这些可能性的路径,若与掌控大多数 AI 技术栈(甚至全部)的公司利益不符,就很可能被封锁。如果某项潜在的 AI 技术有可能通过解决某些产业赖以牟利、甚至具有寄生性质的问题,从而威胁广告收入,那么像谷歌与 Meta 这样的科技公司几乎必然会阻止这一技术进入市场的尝试。
特朗普政府迄今为止最重要的政策举措之一,就是其新的加密货币政策。该政策废除了上一届政府的行政命令,并致力于制定一个有助于推动该技术发展的监管框架。这对于人工智能领域中正在发生的其他形式的创新具有重要意义。有了除了传统风险投资之外的其他资源——例如通证经济(tokenomics)[50],初创公司可以为其项目提供资金支持,并积累发展势能。
彼得·蒂尔在其著作《从零到一》(Zero to One)中提出,初创公司本身就在、也应该在寻求成为垄断者。他们需要在市场中占据一个特定空间,通过开发专有技术击败其他竞争者,并进一步排除后来者进入该市场。正如蒂尔所言,如果企业不想成为失败者,这种策略是至关重要的。若他们希望获得投资者的关注,就必须采取建立垄断地位的路径。然而,借助通证经济以及其他与加密货币相关的机制,人们也有机会开发出有价值的技术,同时保留开源精神。在这样的机制下,合作与协作得以推动,同时也能获得支持增长所需的资金。
Section 3.4 价值能动性
经济能动性之所以被削弱,是因为市场中那些具备质感的价值创造机会正在减少,使个体难以通过创新与生产满足不断变化的需求与欲望。当 AI 技术栈被少数几家垄断企业掌控并主导整个生态系统时,即使有人识别出一个真正有意义的问题,并设计出强有力的解决方案,如果这不符合大型企业的利益,该方案也很可能无法进入市场。经济活动及其所带来的社会价值,不应建立在一套容许权力任意压制、扼杀对社会整体有益事务的权威机制上。那么,AI 垄断企业又是如何压缩人们在价值能动性上的“质性丰富机会”的呢?
如果雷·库兹韦尔的奇点理论及其相关预测哪怕部分属实——如果人类真的将与非生物智能融合,并生活在日益人工化的环境中——那么人工智能的垄断不仅不可取,而且可以说是一种反乌托邦式的局面。这种设想唤起了关于“技术霸主”的画面:他们主宰着人类社会,而人们要么沦为智能机器的奴工,要么则是舒适而满足地享受着智能繁荣所带来的物质成果。在这样的图景中,总有人必须开采矿物资源,而另一些人则消费着由此生产出的丰富商品与服务。但如果我们假设 AI 的发展会快到足以让智能机器人无需人力就能完成矿产开采工作,那最终所有人都会转变为纯粹的“消费者”。“在接下来的几十年里,”库兹韦尔预测,“几乎所有例行性的体力与脑力活动都将被自动化。”届时,唯有那些具有社交性、创造性、创新性或高度不可预测性的工作将对拥有相关技能与培训的人开放,其余人将大多成为消费者。而借助纳米机器人、虚拟现实、非生物智能增强技术与无处不在的信息流动,我们的现实将愈加接近哲学家罗伯特·诺齐克(Robert Nozick)所设想的“体验机”(experience machine)。
通过某种装置的介入——无论是接入某种模拟装置,还是完全沉浸于类似虚拟现实(VR)那样的数字化、信息化环境中——人们可以体验到他们所希望的任何事情。任何感官体验、情绪、思想或事件,都会随时向任何人开放,随时可供消费。一个人可以体验写出“伟大的美国小说”所带来的深刻满足,像苏格拉底[51]那样在雅典法庭上勇敢地对抗陪审团,或像拿破仑那样英勇地站在青翠的高岗上俯瞰敌军,也可以在模拟的攀登中登上珠穆朗玛峰,体会坚持不懈的荣耀与世界之巅的视野。重要的不是这些事件是否真实发生,而是有人“渴望”它,而它就会“存在”。在这样的图景中,人生的目标就是消费;而“道德生活”——值得追求的生活——则被定义为追求内部刺激的生活。外部世界、个体真实的存在状态将不再重要。一个人是否真实地勇敢、富有同情心、充满爱意、公正、虔诚、善良或邪恶——这都不再有意义。人们的兴趣与冲突将在人工体验的消费中得到调和。在一个“问题已被解决”的世界中,没有需要行动者去解决的具体问题,行动者也就变得可有可无;唯一需要的,是“消费”。
这种情境真正危险之处在于,垄断企业将完全掌控生成技术的算法,也即控制我们可接触的信息结构。信息将不断被嵌入到以消费为中心的环境中。理想情况下,人们应当拥有自由,做他们想做的事,以他们认可的方式生活。但人们“看待”世界的方式,他们建构现实的方式,他们所处的社会语境——都会被那些已经整合智能资本、成为未来唯一商品与服务生产者的公司所过滤与塑造。哲学家艾伦·布鲁姆(Allan Bloom)在其著作《美国精神的封闭》(The Closing of the American Mind)中写道:“每一个教育系统都有一个它希望达成的道德目标,并据此构建其课程。它希望塑造出某种特定类型的人。”人工智能的垄断企业将通过改造人的生存环境来塑造“人是什么”的意义,以符合其自身利益。而真正重要的那些事情——运用能动性、实现真实的自我效能感、发现自己在人生中真正珍视与渴望的事物、建构让现实更一贯、宜居和统一的人生目标等等的机会——将被被企业利益所强烈影响和操控。而这些利益,本质上是围绕经济增长与利润最大化构建的。
在诺姆·乔姆斯基(Noam Chomsky)[52]与爱德华·赫尔曼(Edward Herman)[53]合著的《制造共识》(Manufacturing Consent)[54]一书中,两位作者提出,美国媒体实际上是一种宣传工具,而非客观的信息来源(这一观点当时颇具争议,但如今已成为主流看法)。他们认为,这种宣传功能是通过一套“过滤模型”来运作的,该模型将信息作为输入,并为公众“福祉”完美制造出标准化的输出。而其中一些媒体过滤机制,正是今天科技巨头所采用的。第一个过滤器是媒体公司的规模、所有权结构及其以利润为导向的商业模式。这使得进入媒体市场所需的投资与准入成本变得高得惊人,从而使其他竞争者难以生存。法律制度被用来执行一系列标准,这些标准压制了初创公司与中小企业的发展;而政府补贴则倾向于支持那些与政府利益保持一致的媒体公司。第二个过滤器是广告收入。广告不仅提升了特定公司的利润,也让它们在竞争中占据优势。那些无法吸引广告支持的媒体来源往往被市场边缘化。在此过程中,那些资金雄厚的媒体公司为了争取广告商的“青睐”,被迫迎合股东所要求的持续利润增长。这意味着任何挑战企业利益的声音,都可能因营收减少而遭受惩罚,最终被逐出市场竞争。
这两个过滤器,正是当今科技巨头在其平台上运用的机制。他们主导市场,并依靠广告收入获取惊人的利润。正如乔姆斯基与赫尔曼所指出的另一个过滤器——意识形态偏向,大科技公司同样如此。就像上世纪八十年代的主流媒体会大肆报道敌对国家的种族灭绝与谋杀,却对发生在美国“势力范围”如拉美地区的同类事件视而不见,大科技公司也会在符合其经济与利益考量时,沿着特定的意识形态线索行事。由于其庞大的利润模式与动机,大科技公司的利益并不必然与真理、勇气、准确性、诚实、公正或善恶标准一致。只有当这些价值可以带来可预见的利润与效用最大化时,它们才可能被采纳。因此,如果 AI 垄断企业逐步获得市场主导权,并以其最先进模型为基础将大量商品与服务推向市场,那么人们对于世界的理解、他们如何看待现实、哪些事物最值得关注——都会在信息过滤器的引导下被重塑。这些过滤器正是大科技公司用于“产出有利于技术发展结果”的机制的一部分。个体发展自身的机会、形成自我世界观的过程、以及构成生活统一性的价值体系,都将受到科技信息过滤器的支配与重构。
我们很容易想象这样一个世界:信息的生成由一小部分集中的模型主导,这些模型构建出一套相互交织的信息网络,强化着不准确、不诚实、甚至是伪造的信息结构。新闻标题与报道可能散布错误主张与对现实的歪曲,而这些说法又会被其他虚假信息源所“证实”,彼此互为支撑。这种信息结构——即信息的组织方式及其意义赋予机制——可能会被人为策划,以服务于掌握权力与控制信息传播资源者所设定的特定目的。少数人认为“最好的”内容将被优先推送,而公众的想法将逐渐变得从属,最终被操控以符合权力方的利益。这并不是在指责某个实体或个人有恶意意图,而是在强调这样一种结构性困境:当生成并传播社会所消费的信息的能力被集中在少数几方手中时,这种权力格局所带来的难以解决的困境。
这最终将不可避免地导向类似于前文提到的诺齐克“体验机”的世界。人们获得一种超越消费伦理的生活形式能力的机会将被极大压缩,甚至被彻底剥夺。确实,假设未来大多数工作被自动化,人们通过基本收入实现生活保障,那么个体将从劳作的束缚中解放,不再被迫为经济增长贡献劳动力。从某种意义上说,人类将获得对约束与必需品的自由。但问题在于,如果没有施展自由的媒介,如果没有真正的机会在具体经验中运用自己的能动性,那么这种自由就并不是真正的自由——至少不是那种更深层次的、积极意义上的自由。那种引导人们思考“如何生活”、那种通过探索而发现值得投入心力与时间的事业的过程、那种确立人生目标并在充满挑战与刺激的环境中努力实现的能力,将会在这样的结构中逐渐失效,甚至彻底被边缘化。
哲学家约翰·杜威(John Dewey)曾写道:
我们很少意识到,我们对什么有价值、什么无价值的判断,在多大程度上是受制于我们并不自觉的标准。但一般来说,那些我们未经思考便视为理所当然的事物,正是决定我们有意识思维与判断结论的关键。而那些位于反思之下的习性,往往正是在我们与他人的持续互动与交换中形成的。
如果构成社会的制度是由那些以提升股东利润为目的的大型企业所主导——这将在它们主导人工智能时成为现实——那么它们的模型将渗透进经济的每一个领域,渗入我们的环境。这些环境将影响我们所被激发的生活方式,朝向不再体现为实际的‘存在’(being),而是依赖于‘拥有’(having)。也就是说,什么是显著的、值得追求的、具有吸引力的,不再取决于它所需要的努力、它所要求的冒险精神,或它所能激发的成长过程,而是取决于它能否填满并打发时间。对于一种由消费伦理塑造的意识而言,显而易见、理所当然的东西,将与另一种由合作构成、旨在促使个体能动性寻求意义与目标的社会完全不同。前者会看到一个充满各种可能体验的世界,但这些体验除了即时呈现的感受之外毫无意义;而后者则仍然会体验到“必要性”,以及那种不可遏制的冲动——即人必须感受到世界上仍有值得行动之事。赫尔曼·梅尔维尔(Herman Melville)在其伟大的美国小说《白鲸》(Moby Dick)中写下了这样的句子:
我坚定目标的道路铺设着铁轨,我的灵魂被刻槽其上。穿越无底峡谷,穿越山脉深处与激流之下,我直奔而去!没有障碍,没有转弯,只有通向铁轨终点的直路!
但愿,那些曾赋予梅尔维尔写作力量的精神碎片,在未来的某个角落依然得以存在。
Section 3.5
在《查拉图斯特拉如是说》(Thus Spoke Zarathustra)一书中,尼采描绘了两种未来人类的形象:“末人”(Last Man)与“超人”(Overman)。这两者在本能、欲望、动机与驱力方面有着根本性的不同。他们所看到的世界、感知世界的方式也截然不同:哪些事物对他们而言是显著且有意义的,什么是“善”或“恶”,对自我与世界的信念与态度,皆南辕北辙。
尼采对“末人”充满蔑视,而他的理想目标则是“超人”。“末人”代表一种追求舒适、安逸与满足的生活方式——那是一种消费的生活,是一种被动的满足。末人的畜群(herd)沉浸在“白天的微小快乐、夜晚的微小快乐中,但极度重视健康。他们说:‘我们发现了幸福’,眨着眼睛”。这样的存在,培养出的是享乐、安逸、饱足与消费的本能。尼采常将这种状态比喻为“反刍的牛”。而“超人”则是那种能够保有创造与超越本能的存在,他将生命导向某个遥远而艰难的目标,借此创造出一种超出自身的价值,使生活因此获得尊严与意义。超人仍然保有那种穿越变革性经验的冲动,那种能改变自我存在状态与意识体验的本能。正是这种冲动激发个体去掌握现实、理解现实,并因此增强他们影响现实的能力——个体越来越能够通过自己的活动与存在方式去塑造经验,建构世界。“末人”的美德——最大化快乐并最小化痛苦,在“超人”看来,恰恰是堕落的恶德。
人工智能的垄断结构及其以利润为导向的模式,正在推动“末人”的出现;而开源则是在为“超人”保留空间。随着人工智能被集中于少数强权之手,并通过这些权力机构设定的参数向市场大量输出商品与服务,整个信息景观及其传播网络将被精心策划成一种伦理结构——这种伦理以最大满足与持续消费所带来的舒适感为核心。在这样的结构中,个体所接触到的机会与环境将不再是“质感质性丰富”的;它们不会激发人们内在的主动能力,而只会使人变得能够追求一种消费社会所设定的终极目标——即最大化产出与回报的路径。
而开源生态系统,则保留了一个人类能动性仍能找到出口的空间。在那里,创造力与创新的目标不再仅仅是为了逐利,而是为了实现一种更完整的人类生活。
现在,本文开篇提出的一个问题是:自动化是否能带来足够多的机会,使被替代的劳动力能够重新获得工作?到现在我们已经看到,黑客范式与开源生态系统的确让这一目标更为可行。彼得·蒂尔的《从零到一》可以说是一本创业者指南。而他在书中明确指出:创业的目标应当是至少模仿,并努力实现垄断。所谓“成功”,就是在某一市场领域内占据主导地位,排除其他进入者,并通过专属供应尚未满足的需求来实现利润最大化。但成功初创企业的统计数据[55]却令人沮丧。初创企业的失败率高达90%。在那些成功者中,首次创业者只占18%。获得风险投资资金的初创企业不到1%;获得天使投资的比例也不到1%;约有75%的初创公司依赖“信用卡债务、商业贷款与信用额度”来筹集资金。成功的几率微乎其微,而对那些敢于创业,尤其是技术驱动型创业者(这是失败率最高的一类)所需承担的门槛与风险,往往近乎不可逾越。蒂尔之所以鼓励初创企业采用垄断策略,部分原因正是因为唯有在获得足够稳固的市场地位之后,公司才终于能够喘息、拓展与创新。一旦达到垄断标准,企业便能掌控其特定领域(甚至是整个)市场中的价值输出——理论上,这会给企业与消费者双方带来好处。
然而,这种能力最终被集中在极少数能够侥幸成功的公司手中。一旦掌握了这种能力,它们便没有自利的动机去放手。而当某家企业依靠其垄断地位终于获得创新的自由之时,这种专属能力却也意味着其他拥有创造潜力的人被排除在外,仅仅因为他们没有获得那唯一的机会。
如果企业的成功几率更高,那无疑会更具吸引力。但传统的融资方式以及作为成功创业者所需经历的艰难过程,往往会打击甚至扼杀那些本有能力提出改变世界的强大创意的人们。而黑客范式之所以具有深远意义,正是因为它能够提供丰富的机会,让人们得以创造价值,而无需承担传统创业所附带的高风险。黑客范式的“北极星”之一,就是致力于打造一个开放的、无需许可的生态系统——一个充满机会、人们可以自由进入、自由利用关键技术信息,并能够与成熟企业协作,从而共同创造出更好、更具创新性的产品的环境。开放的生态系统能够赋予人们创造价值的可能,而封闭系统则将他人排除在外,关闭了协作的大门。
按照蒂尔模式的创业路径,那是一条崎岖不平的道路。它需要强烈的意志、非凡的创造力,当然还需要一定的运气。而这三者的完美契合,是极其罕见的。因此,真正能在创业中成功的人少之又少。通过一个无需许可的开源生态系统,通过减轻人们在创造有价值事物时所承受的沉重负担,我们可以释放出大量机会——这些机会无需你拥有成为乔布斯或贝索斯那样的雄心与资源,也不要求你必须独力成就一番技术帝国。事实上,那些科技巨头的成功,早已远远超越了他们当初想要创造创新科技的初衷。开源生态系统将推动科技进步的机会民主化,使人们能够真正参与其中,不必成为少数天才企业家的复制品。创新,理应是更具协作性、更广泛分布的,也应当距离普通人更近。黑客范式正在使这成为可能,它正在重构赛场的平衡。
或许,并不是每个人都想成为一名“黑客”。但开源为我们保留并拓展了一种最佳的原型模式,通过它,可以将具体的机会持续地、公平地分配给人们,让他们得以实践自己的能动性。正是通过拥有这类机会,人们仍能发现和体验到那种强烈的召唤感——“我必须去做某事”——即,一个目标的存在,使个体不得不相信,若忽视它,人生就将失去意义与目标。如果我们生活的世界中,人们能接触到的、最显眼且最具吸引力的事物,仅仅是尼采所说的那种“幸福”——那种不涉及个人牺牲、不包含作为德性的献身(devotion)、也无需为艰难而变革性的事业奋斗的意愿的“幸福”——那么这样的世界无疑比不上另一个世界:在那里,人们拥有真正的机会去成就伟大的事业,只要他们愿意去追求。
结语
当 IBM 的“深蓝”在 1997 年击败国际象棋冠军卡斯帕罗夫(Garry Kasparov)时,象棋并未因此被淘汰。人们依旧继续比赛,并不断变得更强。这一事实——即从那以后任何人类棋手都不可能战胜 AI 程序——并未动摇那些热爱象棋之人的热情与动力。那些献身于象棋的人依旧渴望打磨自己的技艺,学习更复杂的策略,在不断成长的过程中超越其他选手。象棋选手依然渴望变得更优秀,仅仅是为了变得更优秀。通过意志与投入实现成长,当他们登上新的水平时,那种深刻的成就感依旧真实而宝贵,尽管一台机器将永远是更强的选手。 在一部关于李世石(Lee Sedol)在 2016 年败给 AlphaGo 的纪录片中,有人说:“他在这台机器的对弈中获得了成长。他的人性在与这台无生命的创造物对局之后得到了拓展。而我们的希望,是这种机器,尤其是背后的技术,也能对我们所有人产生同样的作用。”还有人说:“或许 AlphaGo 能向人类展示一些我们从未发现过的东西。或许那是一种美。”如果被正确使用,人工智能可以拓展个体影响与改变世界的能力。它可以提供创造的机会,而非只是劳作的义务;可以唤起意义的体验,而非冷漠与疏离;可以使人获得一种有价值的自由,而非无所依托的自由。但这一切都取决于社会写作和去推动人们向值得努力实现的目标前进的环境;它也要求我们以不同的方式理解竞争。
Agency/Agent/Agentic/… 能动性 Being (以…方式)存在 Qualitatively Rich 质性(上)丰富 Open Source Ecosystem 开源生态系统 Proprietary 专有 Pleasure 快乐 Happiness 幸福 所有著作、节目与人物名称第一次出现标记英文原文。 除网站链接之外的脚注,均为译者补充;脚注中的外部链接为原文超链接的对应标记。 原文中的特殊格式均保留在中文对应词项中。
参考文献
[1] 美国人工智能理论家、作家,MIRI(Machine Intelligence Research Institute,机器智能研究所)创始人之一。 [2] 俄罗斯裔美国计算机科学家,路易斯维尔大学教授,专长于AI安全和人工智能伦理。 [3] 瑞典裔美国物理学家、MIT教授,Future of Life Institute(未来生命研究院)联合创办人。 [4] https://futureoflife.org/open-letter/pause-giant-ai-experiments/. [5] https://a16z.com/the-techno-optimist-manifesto/.硅谷知名风险投资家、网景(Netscape)浏览器联合创始人,Andreessen Horowitz投资公司创始人。 [6] https://ia.samaltman.com/. OpenAI CEO. [7] 发明家、未来学家、作家,现为谷歌工程总监。 [8] 特斯公司CEO,SpaceX创始人兼首席执行官,X(原Twitter)所有人。 [9] HAL 9000(简称HAL)是科幻小说和电影系列《太空奥德赛》中的虚构人工智能角色,由阿瑟·克拉克(Arthur C. Clarke)和斯坦利·库布里克(Stanley Kubrick)共同创作。在作品中,HAL 9000原本是飞船“发现号”(Discovery One)的中央控制系统,它被设计得极其可靠,拥有高度智能、情感模拟能力,负责飞船运行,包括导航、生命支持、通信等核心任务。在执行任务时,由于HAL开始表现出微妙的异常(如错误报告设备损坏),同行宇航员决定关闭HAL。当这一计划被HAL得知,HAL控制飞船上设备造成了同行宇航员的死亡。但后续作品揭示,HAL的表现是由于收到了相互冲突的人类指令,并决定杀死宇航员来保证两种指令都能够实现。 [10] 法国经济学家。 [11] 美国经济和社会理论家、作家、公众演说家、政治顾问和活动家。 [12] 经济学家、教授,现任斯坦福大学数字经济实验室主任。 [13] 研究员、作家,MIT斯隆管理学院副教授、MIT数字经济计划副主任。 [14] http://digamo.free.fr/brynmacafee2.pdf/ [15]https://www.brookings.edu/articles/rising-inequality-a-major-issue-of-our-time/ [16] 硅谷投资人,PayPal创始人,企业家、风险投资家、政治思想家、作家。 [17] 经济学家、哲学家、道德理论家,古典经济学奠基人。 [18] 芬兰哲学家。 [19] 社会学家、经济学家、历史学家、政治学理论家,德国社会学与历史学传统的代表人物之一,被称为现代社会学的奠基人之一。 [20] http://www.catb.org/esr/faqs/hacker-howto.html [21] 这三个词的区别在斯密研究中并没有得到广泛讨论。一些学者认为它们是同义的,通过重复表达强调(参考J.Z. Muller, (1993) Adam Smith in His Time and Ours: Designing the Decent Society, New York: Free Press第69页,Willie Henderson and Warren J. Samuels, (2004) The etiology of Adam Smith’s division of labor, in Essays on the History of Economics)。就这三个词在英语中的使用历史而言,truck system在英国曾经意为用实物作为工资的薪资制度,barter通常指不涉及货币的物物交换。 [22] Eric Fromm, Marx's Concept of Man. [23] 古希腊哲学家。 [24]https://happyheartfamilies.citymax.com/f/Self_Efficacy.pdf [25]https://happyheartfamilies.citymax.com/f/Self_Efficacy.pdf [26] 一个专注于在线支付处理和金融基础设施的平台,帮助企业在互联网上管理资金流动。 [27]https://www.applogicnetworks.com/blog/sandvines-2024-global-internet-phenomena-report-global-internet-usage-continues-to-grow [28]https://www.emarketer.com/learningcenter/guides/amazon-revenue/ [29]https://cxotoday.com/news-analysis/big-tech-to-own-two-thirds-of-world-data/#:~:text=Without%20sounding%20like%20a%20predictor%20of%20doomsday%2C,data%20centers%20while%20the%20rest%20is%20on [30]https://botpopuli.net/digging-deeper-assessing-big-techs-capture-of-the-internets-infrastructure/#:~:text=The%20dominance%20of%20Big%20Tech,Services%20(AWS)%20in%202006. [31]https://academic.oup.com/policyandsociety/advance-article/doi/10.1093/polsoc/puae012/7636223 [32]https://finance.yahoo.com/news/big-tech-set-to-invest-325-billion-this-year-as-hefty-ai-bills-come-under-scrutiny-182329236.html [33]https://www.technologyreview.com/2023/12/05/1084393/make-no-mistake-ai-is-owned-by-big-tech/ [34]https://academic.oup.com/policyandsociety/advance-article/doi/10.1093/polsoc/puae012/7636223 [35]https://academic.oup.com/policyandsociety/advance-article/doi/10.1093/polsoc/puae012/7636223 [36]https://www.technologyreview.com/2023/12/05/1084393/make-no-mistake-ai-is-owned-by-big-tech/ [37] 硅谷知名投资人,安德森·霍洛维茨基金(Andreessen Horowitz,简称a16z)的普通合伙人(General Partner)。 [38]https://a16z.com/why-deepseek-is-a-gift-to-the-american-people/ [39]https://www.federalregister.gov/documents/2023/11/01/2023-24283/safe-secure-and-trustworthy-development-and-use-of-artificial-intelligence [40] 美国著名记者、专栏作家,独立新闻平台自由新闻(The Free Press)的创办人。 [41]https://darioamodei.com/on-deepseek-and-export-controls [42] 半导体行业分析师,SemiAnalysis网站创始人。 [43] AI研究员、工程师。 [44]https://www.youtube.com/watch?v=TcJtvzF-FP8&t=2736s [45]http://www.northamericannietzschesociety.com/uploads/7/3/2/5/73251013/nietzscheana5.pdf [46] https://en.wikipedia.org/wiki/Agon [47] 霍布斯的《利维坦》(Leviathan)中对自然状态下的人的生活的刻画。 [48] 安德森·霍洛维茨基金普通合伙人,负责加密货币与Web3投资部门(a16z crypto)。 [49] 比特币(Bitcoin)的创造者,身份不明。 [50] 也译为“代币经济学”,是对加密货币或区块链项目的经济层面的研究和分析,尤其关注其原生数字代币的设计和发行。该术语由“代币/通证”(token)和“经济学”(economics)两个词组合而成。 [51] 古希腊哲学家。 [52] 美国教授和公共知识分子,以其在语言学、政治活动和社会批评领域的研究而闻名。乔姆斯基有时被称为“现代语言学之父”,他也是分析哲学的重要人物和认知科学领域的创始人之一。 [53] 美国经济学家、媒体学者和社会评论家。 [54] https://focalizalaatencion.wordpress.com/wp-content/uploads/2012/08/herman-chomsky-2002-manufacturingconsent.pdf [55] https://explodingtopics.com/blog/startup-failure-stats
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 9223d2fa:b57e3de7
2025-04-15 02:54:00
@ 9223d2fa:b57e3de7
2025-04-15 02:54:0012,600 steps
-
 @ 7e8ca676:b6a7569f
2025-05-13 01:47:06
@ 7e8ca676:b6a7569f
2025-05-13 01:47:06There was a time when Bitcoin smelled like ozone and rebellion. When men wore hoodies because they meant it. When software didn’t come with a mission statement or a DAO-approved pronoun guide. When the only thing a Bitcoin dev feared was being wrong, not being unpopular. \ \ That time is dead. \ \ It died somewhere between the fifth Twitter thread explaining why putting JPEGs on the base layer was “valid use,” and the fiftieth PR that added complexity to the engine in order to simplify the cupholders. Now we’re here, ankle-deep in a pool of our own mediocrity, arguing over whether we should triple the OP_RETURN limit so a VC-backed sidechain company can offload its plumbing costs onto your Raspberry Pi. \ \ Welcome to the future. It’s paved in GitHub comments and smells like a WeWork bathroom. \ \ Let’s speak plainly. This whole drama is not about OP_RETURN. It’s about power. Not electrical power. Not hash power. Soft power. The power to redefine what Bitcoin is for, one pull request at a time. It is the power to turn the protocol from a blunt, uncompromising monetary weapon into a polite corporate middleware bus for protocol startups that couldn’t raise a Series B without a little help from their friends in Core. \ \ Jameson Lopp wants to increase the OP_RETURN limit. Why? Because his company, Citrea, needs to squeeze a few more bytes into every transaction. It's not a crime. It’s not even dishonest. It's just pathetically on the nose. They don’t want to pay miners directly. They want the mempool to be their free emergency broadcast system. They want to lean on the public infrastructure without sending flowers or even a thank-you note. \ \ And what does Core say? \ \ They say yes. \ \ Because of “technical merit.” \ \ Because it’s “more efficient.” \ \ Because the devs have long since stopped being guardians of the protocol and started being unpaid product managers for whoever can string enough buzzwords together in a conference talk. \ \ You can see it in their eyes. You can hear it in their interviews. The Core devs aren’t building Bitcoin anymore. They’re managing Bitcoin. They’re curating it. Polishing it. Nerfing it for mass adoption. Like a bunch of Brooklyn baristas trying to make espresso kid-friendly. Bitcoin used to be an espresso shot poured directly into the mouth of the Federal Reserve. Now it’s a lukewarm latte with oat milk and consensus-breaking sprinkles. \ \ The worst part? The refusal to acknowledge that this is not about UTXO bloat. It's not about cleaner mempools. It’s about upstreaming corporate convenience into the base layer under the halo of neutrality. It’s about giving polite names to ugly compromises. “Policy adjustment.” “Ergonomic improvement.” “Relay optimization.” They speak in this weird dialect of bureaucratic techspeak that means nothing and does less. \ \ Meanwhile, the only thing that actually matters gets lost: ossification. \ \ The holy grail of this protocol is ossification. Not stagnation. Not laziness. Not gridlock. Just stability. The longer Bitcoin can go without consensus changes, the more credible it becomes. The more unchangeable it becomes. Like gravity. Like rust. It doesn’t matter how good your argument is. The system won’t budge. That’s the point. The value of Bitcoin isn’t in how clever the devs are. It’s in how irrelevant they become. \ \ But ossification isn't something you declare. You sneak up on it. You approach it sideways, like a wild animal. You do less and less until eventually you’re doing nothing at all, and nobody even remembers how to change the code anymore. That is the goal. To make the protocol so boring, so petrified, that no one can move it. Not Lopp. Not Luke. Not even Larry from Legal. \ \ To get there, we need something devs hate: client balkanization. \ \ That means splitting the client into pieces. Break the codebase. Separate the consensus engine from the policy fluff. Let people run different implementations. Let the free market decide what filters they want, what mempool rules they tolerate, what behavior they’re willing to relay. You want a node that bans inscriptions? Run it. You want a client that auto-forwards every transaction with a JPEG of your left toe? Go for it. Just don’t make it my problem. \ \ Right now, Bitcoin Core is a monoculture. It’s the cathedral and the altar and the pamphlet all rolled into one. That’s not healthy. That’s a single point of failure. That’s a priesthood. \ \ And no, Bitcoin isn’t a religion. It’s worse. It’s a culture. Religion has rituals. Culture has habits. And habits are harder to break. Especially when your dev team gets drunk on the idea that their opinions are features. \ \ If you want to fix this mess, you need to kill the idea that Bitcoin Core is the final word. Strip it down. Remove every line of non-consensus code. Make it boring. Make it dumb. Let the client rot in peace, and let a thousand weird little nodes bloom. \ \ Let the spammers spam themselves into oblivion. Let the free-riders find someone else to subsidize their infrastructure. Let every operator set their own damn filters. \ \ You’ll know ossification is working when the devs start getting bored. When they stop showing up. When there are no more debates. When the politics dry up. When Jameson Lopp finally logs off. \ \ Until then, every line of code you don’t remove is a future argument you’ll be forced to have with someone who thinks “data availability” is more important than keeping the protocol boring. \ \ Bitcoin does not need to be exciting. It needs to be a brick. A self-righteous, opinionated, uncompromising, utterly stubborn monetary brick. \ \ Keep your hands off it. \ \ And take your startup with you.OP_RETURN and the Cult of Cleverness: Or, How Bitcoin Core Learned to Love the Smell of Its Own Farts
There was a time when Bitcoin smelled like ozone and rebellion. When men wore hoodies because they meant it. When software didn’t come with a mission statement or a DAO-approved pronoun guide. When the only thing a Bitcoin dev feared was being wrong, not being unpopular.
That time is dead.
It died somewhere between the fifth Twitter thread explaining why putting JPEGs on the base layer was “valid use,” and the fiftieth PR that added complexity to the engine in order to simplify the cupholders. Now we’re here, ankle-deep in a pool of our own mediocrity, arguing over whether we should triple the OP_RETURN limit so a VC-backed sidechain company can offload its plumbing costs onto your Raspberry Pi.
Welcome to the future. It’s paved in GitHub comments and smells like a WeWork bathroom.
Let’s speak plainly. This whole drama is not about OP_RETURN. It’s about power. Not electrical power. Not hash power. Soft power. The power to redefine what Bitcoin is for, one pull request at a time. It is the power to turn the protocol from a blunt, uncompromising monetary weapon into a polite corporate middleware bus for protocol startups that couldn’t raise a Series B without a little help from their friends in Core.
Jameson Lopp wants to increase the OP_RETURN limit. Why? Because his company, Citrea, needs to squeeze a few more bytes into every transaction. It's not a crime. It’s not even dishonest. It's just pathetically on the nose. They don’t want to pay miners directly. They want the mempool to be their free emergency broadcast system. They want to lean on the public infrastructure without sending flowers or even a thank-you note.
And what does Core say?
They say yes.
Because of “technical merit.”
Because it’s “more efficient.”
Because the devs have long since stopped being guardians of the protocol and started being unpaid product managers for whoever can string enough buzzwords together in a conference talk.
You can see it in their eyes. You can hear it in their interviews. The Core devs aren’t building Bitcoin anymore. They’re managing Bitcoin. They’re curating it. Polishing it. Nerfing it for mass adoption. Like a bunch of Brooklyn baristas trying to make espresso kid-friendly. Bitcoin used to be an espresso shot poured directly into the mouth of the Federal Reserve. Now it’s a lukewarm latte with oat milk and consensus-breaking sprinkles.
The worst part? The refusal to acknowledge that this is not about UTXO bloat. It's not about cleaner mempools. It’s about upstreaming corporate convenience into the base layer under the halo of neutrality. It’s about giving polite names to ugly compromises. “Policy adjustment.” “Ergonomic improvement.” “Relay optimization.” They speak in this weird dialect of bureaucratic techspeak that means nothing and does less.
Meanwhile, the only thing that actually matters gets lost: ossification.
The holy grail of this protocol is ossification. Not stagnation. Not laziness. Not gridlock. Just stability. The longer Bitcoin can go without consensus changes, the more credible it becomes. The more unchangeable it becomes. Like gravity. Like rust. It doesn’t matter how good your argument is. The system won’t budge. That’s the point. The value of Bitcoin isn’t in how clever the devs are. It’s in how irrelevant they become.
But ossification isn't something you declare. You sneak up on it. You approach it sideways, like a wild animal. You do less and less until eventually you’re doing nothing at all, and nobody even remembers how to change the code anymore. That is the goal. To make the protocol so boring, so petrified, that no one can move it. Not Lopp. Not Luke. Not even Larry from Legal.
To get there, we need something devs hate: client balkanization.
That means splitting the client into pieces. Break the codebase. Separate the consensus engine from the policy fluff. Let people run different implementations. Let the free market decide what filters they want, what mempool rules they tolerate, what behavior they’re willing to relay. You want a node that bans inscriptions? Run it. You want a client that auto-forwards every transaction with a JPEG of your left toe? Go for it. Just don’t make it my problem.
Right now, Bitcoin Core is a monoculture. It’s the cathedral and the altar and the pamphlet all rolled into one. That’s not healthy. That’s a single point of failure. That’s a priesthood.
And no, Bitcoin isn’t a religion. It’s worse. It’s a culture. Religion has rituals. Culture has habits. And habits are harder to break. Especially when your dev team gets drunk on the idea that their opinions are features.
If you want to fix this mess, you need to kill the idea that Bitcoin Core is the final word. Strip it down. Remove every line of non-consensus code. Make it boring. Make it dumb. Let the client rot in peace, and let a thousand weird little nodes bloom.
Let the spammers spam themselves into oblivion. Let the free-riders find someone else to subsidize their infrastructure. Let every operator set their own damn filters.
You’ll know ossification is working when the devs start getting bored. When they stop showing up. When there are no more debates. When the politics dry up. When Jameson Lopp finally logs off.
Until then, every line of code you don’t remove is a future argument you’ll be forced to have with someone who thinks “data availability” is more important than keeping the protocol boring.
Bitcoin does not need to be exciting. It needs to be a brick. A self-righteous, opinionated, uncompromising, utterly stubborn monetary brick.
Keep your hands off it.
And take your startup with you.
-
 @ 961e8955:d7fa53e4
2025-05-13 06:25:13
@ 961e8955:d7fa53e4
2025-05-13 06:25:13Cryptocurrency has been a buzzword for some time now, and Turkey is one of the countries that have been actively involved in the crypto market. However, the Turkish government has recently introduced new regulations on cryptocurrency trading and mining. This article aims to provide you with an overview of the cryptocurrency regulations in Turkey and some investor tips to navigate the market.
Overview of Cryptocurrency Regulations in Turkey

The Central Bank of the Republic of Turkey (CBRT) and the Capital Markets Board of Turkey (CMB) are the two regulatory bodies that oversee the cryptocurrency market in Turkey. Here are some of the recent regulations introduced by the Turkish government:
Ban on Cryptocurrency Payments: In April 2021, the CBRT banned the use of cryptocurrencies for payment transactions in Turkey. This means that businesses are not allowed to accept payments in cryptocurrencies such as Bitcoin, Ethereum, and Litecoin.
Regulation of Crypto Exchanges: The CMB introduced regulations in May 2021 that require all cryptocurrency exchanges operating in Turkey to register with the CMB. Crypto exchanges must also meet certain criteria, such as having a minimum capital of 50 million Turkish Lira ($5.8 million) and complying with anti-money laundering regulations.
Ban on Crypto Mining: In May 2021, the Turkish government announced a ban on cryptocurrency mining. This is due to concerns about the environmental impact of mining, as well as the potential for illegal activities such as money laundering.
Investor Tips for Cryptocurrency Trading in Turkey
Understand the Regulations: It is crucial for investors to understand the regulations surrounding cryptocurrency trading and mining in Turkey. Investors must ensure that they comply with all the requirements set by the regulatory bodies to avoid penalties or legal issues.
Choose a Regulated Crypto Exchange: Investors must only use regulated cryptocurrency exchanges that are registered with the CMB. Regulated exchanges are more likely to follow best practices and protect the interests of their users.
Be Careful with Cryptocurrency Mining: As mentioned earlier, cryptocurrency mining is banned in Turkey. Investors must be cautious about investing in any mining operations within Turkey as they may face legal action.
Do Your Research: Before investing in any cryptocurrency, investors must conduct thorough research to understand the risks and potential rewards of their investment. They should also keep up-to-date with the latest developments in the cryptocurrency market and regulations in Turkey.
Be Mindful of Taxes: The Turkish government taxes cryptocurrency trading profits, and investors must report their earnings from cryptocurrency trading in their tax returns.
Conclusion Cryptocurrency regulations in Turkey have recently become more stringent, and investors must take extra precautions to ensure they comply with all the requirements. Investors must only use regulated cryptocurrency exchanges, understand the regulations, do their research, be mindful of taxes, and avoid cryptocurrency mining operations within Turkey. By following these tips, investors can navigate the Turkish cryptocurrency market and make informed investment decisions.
-
 @ 6e0ea5d6:0327f353
2025-04-14 15:11:17
@ 6e0ea5d6:0327f353
2025-04-14 15:11:17Ascolta.
We live in times where the average man is measured by the speeches he gives — not by the commitments he keeps. People talk about dreams, goals, promises… but what truly remains is what’s honored in the silence of small gestures, in actions that don’t seek applause, in attitudes unseen — yet speak volumes.
Punctuality, for example. Showing up on time isn’t about the clock. It’s about respect. Respect for another’s time, yes — but more importantly, respect for one’s own word. A man who is late without reason is already running late in his values. And the one who excuses his own lateness with sweet justifications slowly gets used to mediocrity.
Keeping your word is more than fulfilling promises. It is sealing, with the mouth, what the body must later uphold. Every time a man commits to something, he creates a moral debt with his own dignity. And to break that commitment is to declare bankruptcy — not in the eyes of others, but in front of himself.
And debts? Even the small ones — or especially the small ones — are precise thermometers of character. A forgotten sum, an unpaid favor, a commitment left behind… all of these reveal the structure of the inner building that man resides in. He who neglects the small is merely rehearsing for his future collapse.
Life, contrary to what the reckless say, is not built on grand deeds. It is built with small bricks, laid with almost obsessive precision. The truly great man is the one who respects the details — recognizing in them a code of conduct.
In Sicily, especially in the streets of Palermo, I learned early on that there is more nobility in paying a five-euro debt on time than in flaunting riches gained without word, without honor, without dignity.
As they say in Palermo: L’uomo si conosce dalle piccole cose.
So, amico mio, Don’t talk to me about greatness if you can’t show up on time. Don’t talk to me about respect if your word is fickle. And above all, don’t talk to me about honor if you still owe what you once promised — no matter how small.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 7e8ca676:b6a7569f
2025-05-13 01:08:28
@ 7e8ca676:b6a7569f
2025-05-13 01:08:28There was a time when mining meant something. Not just the noise of fans and the stink of ozone, but a political act. An act of rebellion, like smuggling pamphlets under the nose of the king. You mined in the basement. You mined with pride. You mined because you could. Not because Fidelity wrote a whitepaper on it. Not because a hosting provider in Iceland offered you a bulk discount. But because you believed.
That miner is dead.
He didn’t die in a blaze of glory. He didn’t go down swinging. He was euthanized. Slowly, over years, by spreadsheets, subsidies, and a thousand tiny concessions. Killed off by a culture that said, “Why do it yourself when you can outsource the soul of Bitcoin to a pool in Singapore?”
Welcome to the age of industrial Bitcoin: a world where miners don’t mine, pools don’t just process. They rule. And the only thing sovereign anymore is the dividend.
The Sovereign Miner is Dead, And No One Mourned
The sovereign miner, the madman with a dusty rack, a full node, and a middle finger pointed squarely at the Eccles Building, is extinct. He’s gone the way of the dodo, the blacksmith, the outlaw. And in his place? A fleet of khaki-wearing ASIC clerks uploading hashrate reports to their VC lords like dutiful little interns. These are not revolutionaries. They are box operators. Corporate larvae wiggling around in server farms financed by pension funds.
Once upon a time, mining was an act of insubordination. You ran a rig to say "no" to Janet Yellen. You ran a node because you meant it. You didn’t need permission. You didn’t ask for subsidies. You didn’t file paperwork. You fought for consensus by living it. Every block was a punch thrown in a quiet, bloodless rebellion. Now? Now you’ve got KPMG-certified mining outfits measuring ESG impact and tweeting about carbon offsets like they’re trying to win a grant from the UN.
The eulogies for that old miner are full of oily euphemisms. They drone on about "efficiency," as if selling your vote for a cheaper power bill is some kind of virtue. "Economies of scale," they whisper, as though scale were some holy sacrament instead of the Trojan horse that delivered centralization to our doorstep. What they call progress, I call a back-alley mugging of Bitcoin’s soul.
The modern miner isn’t mining. He’s leasing his dignity to a pool that doesn’t know his name. He’s plugging in Bitmain boxes like a hotel maintenance worker changing light bulbs. The only heat he generates is for the benefit of someone else's node. Someone else's mempool. Someone else's idea of consensus. He doesn’t build the block. He just pays the electric bill.
And the worst part? He likes it. He thinks it’s normal. He thinks it’s “smart business.” He’s internalized the defeat so completely he brags about it on social media. He’ll tweet about uptime, about efficiency ratios, about hashprice curves—as if he were describing a well-run gulag. He’s the obedient prisoner who polishes the chains and calls it freedom.
The sovereign miner didn’t die in a blaze of glory. He died quietly, smothered under a fleece blanket of comfort and yield optimization. And no one mourned. No one wept. Because everyone was too busy benchmarking their ROI and counting fiat. The revolution didn’t end in a shootout. It ended in quarterly earnings calls.
Power Reversed: Pools Run Nodes, Miners Run Cable
Let’s be crystal clear: The pools run the nodes. The miners do not. This is not a subtle shift. It is a total inversion of power. A coup d'état wrapped in JSON-RPC and relayed with a smile. The pool clerks have become the governors of consensus, and the miners? They’re errand boys. They might control the heat, but they don’t control the protocol. They’re like engine pistons in a car they’ll never be allowed to drive.
Pointing hash at a pool and calling yourself sovereign is like renting a tux and declaring yourself royalty. It’s cosplay. At best. Pools decide what transactions are valid. Pools enforce the rules. Pools interpret consensus, not the miners, not the miners, and certainly not the plebs stacking sats on Raspberry Pis, who, through their economic activity and validation, still enforce the rules but are powerless to stop this creeping centralization in the mining layer. In a world obsessed with decentralization theater, pools are the centralized prop masters pulling the strings.
And when the curtain pulled back in 2021, it wasn’t some secret backroom scandal. No. Marathon Digital bragged about OFAC-compliant mining. They filtered transactions with state-sanctioned precision. They announced it like a new feature rollout. “Censorship-as-a-Service, now in beta!” The mining pool became an extension of the U.S. Treasury—while still waving the Bitcoin banner.
That wasn’t a red flag. That was a blood-soaked banner waved from the parapets of captured consensus. And the response? Nothing. No mass exit. No fork. No slash-and-burn rebellion. Just soft mewling from miners who’d already convinced themselves this was “pragmatic.”
Miners didn’t revolt. They shrugged. They shrugged because they didn’t feel it in their bones anymore. They’d been domesticated. Fattened on subsidies and mining-as-a-service. Pacified by dashboards and yield spreadsheets. When the pools took the steering wheel, the miners reached for the air conditioning controls.
This is the hard truth: sovereignty cannot be delegated. You don’t get to outsource rebellion. You don’t get to file a ticket and request autonomy. If someone else runs the node, someone else owns the power. And if you’re pointing hash at their rules, you’re not free. You’re furniture. Industrial-grade silicon furniture humming in tune with someone else’s politics.
ASICs Are Treadmills, Not Weapons
Here’s a bitter pill: plugging in an ASIC doesn’t make you a participant in Bitcoin. It makes you a battery. Yes, economic nodes still set the rules through their validation and transaction activity. But what happens when the mining layer, the muscle that enforces those rules on-chain, goes rogue? What happens when the mempool you built gets ignored because your hashpower is pointed at someone else's filter?
A node might define validity, but without aligned mining, it’s a lion without teeth. If economic consensus is the blueprint, mining is the builder. And right now, most builders are following someone else's floor plan. The node might say, "this is how we build," but the pool, with its centralized relay and selective enforcement, says, "this is what we’re willing to build."
Without a node, without building your own block, without choosing your own mempool, you’re a hamster in a high-voltage wheel. All that heat and noise? It’s not rebellion. It’s treadmill sweat.
Without a node, without building your own block, without choosing your own mempool, you’re a hamster in a high-voltage wheel. All that heat and noise? It’s not rebellion. It’s treadmill sweat.
You are not a general. You are a grunt. A CPU on contract to someone else’s war.
Fiat Habits: The Culture of Convenience
Bitcoin was supposed to be the great divorce from fiat thinking, a severance from the debt-ridden clown world where every moral principle is for sale if the yield’s high enough. But lo and behold, the fiat habits came slithering in through the miner’s back door. It started small. “Just a hosting service,” they said. “Just outsourcing the firmware,” they claimed. “Just using a pool for efficiency.” And before you knew it, the average miner was indistinguishable from a middle manager at an Enron reunion. Optimizing, spreadsheeting, begging for subsidies like a lobbyist on his third bourbon.
The culture is poison. It rewards cowardice, convenience, and cost-shifting. Small miners moan about volatility like day traders with arthritis. Big miners wine and dine regulators, sniffing after tax incentives and ESG badges like some filthy dog begging at the World Economic Forum’s dinner table. We’re no longer talking about building a sovereign financial system—we’re talking about quarterly earnings, power purchase agreements, and whether your server farm meets carbon neutrality guidelines. What the hell happened?
Take a look back at the New York Agreement in 2017. That wasn’t a negotiation. It was a ransom note. The largest mining outfits, including BTC.Top and ViaBTC, held SegWit hostage because it didn’t butter their bread. The principles didn’t matter. The technical merit didn’t matter. All that mattered was leverage, yield, and preserving their own stranglehold. They tried to shove a hard fork down Bitcoin’s throat like a goose being force-fed for foie gras. And if not for the sheer stubbornness of the user base, real economic nodes who still gave a damn, Bitcoin would’ve gone full Frankenstein.
But did those miners learn? No. They just shifted tactics. Today they ask for different forms of convenience: not block size increases, but subsidies, regulations tailored to their rigs, public-private partnerships. The song remains the same. It’s the fiat mindset dressed up in ASIC drag. Instead of defending neutrality, they demand special treatment. Instead of embracing the responsibility of consensus participation, they’d rather hand it off to a pool that promises good customer service and a Discord server with emojis.
What we’re seeing is the spiritual sequel to fiat monetary policy—moral hazard in overclocked silicon. Miners begging for insulation from the market, protection from volatility, and someone else to carry the political weight of consensus. That’s not sovereignty. That’s serfdom with a spreadsheet. These aren't rebels. They’re corporate supplicants doing yield gymnastics while the heart of Bitcoin withers under the fluorescent lights of their co-location facility.
Bitcoin doesn’t need more efficient parasites. It needs fewer of them. The culture must shift from comfort to combat. From optimization to obligation. A miner who outsources consensus is no better than a fiat printer optimizing bond auctions. The minute you make convenience your god, you become indistinguishable from the system Bitcoin was meant to destroy.
The Culture of Convenience
Bitcoin was born as a rejection of fiat habits. So naturally, miners dragged every last fiat habit into the server farm like rats carrying plague. Outsource the firmware. Outsource the hosting. Outsource the power contract. Outsource the node. Outsource the sovereignty. What’s left?
Mining today looks like Goldman Sachs cosplay. ESG reports. Carbon credits. Webinars on regulatory compliance. Bitcoin isn't being mined anymore. It's being monetized. It's being lobotomized by yield-chasers and spreadsheet cultists.
The New York Agreement was the test. The miners failed. They held the protocol hostage for a slightly thicker block and a fat slice of yield. They were willing to hard fork Bitcoin into a Frankenstein fiat-friendly platform if it meant a better power purchase agreement.
They haven't changed. They’ve just gotten better at disguising their cowardice as competence.
Software Will Not Save You (But Cowards Sure Will Sell You the Illusion)
Let me tell you a ghost story. A tale of silicon treachery dressed up as innovation. It was 2017. The air stank of backroom deals and nervous sweat. Bitmain, the ASIC kingpin of the age, had quietly embedded a little something into its hardware. A cheat code. A hidden rake. A parasitic exploit called ASICBoost, but not the honest kind. No, this was the covert variant, slinking beneath the protocol’s floorboards, exploiting transaction ordering for a tidy little edge. It wasn’t disclosed. It wasn’t debated. It was used. Quietly. Gleefully. While the rest of the ecosystem was busy arguing about scaling like philosophers in a house fire.
Bitmain wasn't interested in consensus. It was interested in arbitrage. They saw Bitcoin not as a commons, but as a slot machine they had rigged. And when SegWit appeared, when it offered scaling and immunity to covert ASICBoost in one surgical tweak, Bitmain panicked. Because SegWit would end the grift. Not softly. Not eventually. Immediately.
So they did what every entrenched parasite does when exposed. They lied. They stalled. They "compromised." They ginned up support for SegWit2x, not to scale Bitcoin, but to preserve their exploit. A hard fork with extension blocks would keep the legacy block structure alive and well, tucked into a cozy parallel track where covert ASICBoost could still thrive. It was a bait-and-switch. A con. A trojan upgrade smuggled in under the banner of progress.
But this time, the hosts fought back.
Node runners saw the ploy. They didn’t need fancy tooling. They needed guts. They didn’t negotiate. They didn’t flinch. They ran SegWit. They activated UASF. They drew a line—not in sand, but in bedrock. Bitcoin would not be held hostage by ASIC cartels. It would not bend for Bitmain. It would not become an extension block casino for rent-seekers in Shenzhen.
So no, software didn’t save Bitcoin. Men did.
Ordinary plebs with full nodes and no backdoor. They used the tool, yes, but what mattered is that they refused. Refused the scam. Refused the deal. Refused to bend the knee to an ASIC cartel dressed in business-casual and lies.
SegWit didn’t win because it was elegant. It won because enough people had the guts to jam it through in spite of sabotage. The protocol gave them a knife, and they had the moral clarity to use it. That’s the lesson. Not that we need better code, but that we need sharper men.
Because in the end, every exploit is possible when the culture is weak. And every fix is worthless if the people implementing it don’t care. The problem was never ASICBoost. The problem was what miners were willing to do to keep it.
The Pool Cartel is the New Central Bank
Middlemen were supposed to die in 2009. That’s the entire reason Bitcoin exists. To gut them. To render them obsolete. To salt the earth behind them so nothing like them could ever grow again. But here they are, reborn, not as banks, but as pools. Not in suits, but in server racks. They wear the garb of "infrastructure providers," but they function as gatekeepers, choke points wrapped in API documentation.
Pools don’t just process, they decide. They decide what gets into the chain. They decide whose transactions are valid. They decide what software matters, and what consensus looks like. They’ve become the central banks of the hashrate economy: unaccountable, invisible, and too boring to fear until it’s too late.
They don’t win power. They absorb it. They don’t need legislation or signatures. They just need you to keep pointing your hash in their direction. That’s the magic trick of middlemen: their power lies in being taken for granted. And in that, they’re the perfect parasite, one that feeds on your energy and then tells you they’re helping you digest it.
Every time you optimize for pool payout efficiency, every time you default to the biggest provider, every time you accept their mempool instead of building your own, you’re kneeling. You’re pledging allegiance to a cartel of block-builders whose loyalty isn’t to Bitcoin, it’s to operational ease and regulatory appeasement.
These aren’t neutral actors. They’re political animals. They hold the levers of consensus without bearing any of its weight. They’re the mortgage-backed securities of Bitcoin: abstracted, opaque, and one market panic away from becoming a systemic risk. We have, once again, created a class of intermediaries who profit by extracting value from a system they didn’t build and no longer understand.
Bitcoin didn’t kill the middlemen. It fed them. It made them smarter. It made them less visible. But their hunger hasn’t changed. And until we name them for what they are—cartels in priestly robes—we will keep mistaking the cage for the cathedral.
Stratum v2: A Rifle, Not a Revolution
Stratum v2 is the closest thing to a loaded weapon Bitcoin miners have been handed in a decade. It is, quite literally, the mechanism by which miners can wrench their dignity back from the clenched fists of the pool cartel. And what have they done with it? Mostly shrugged. A few pilot programs, some halfhearted integrations, and a handful of blog posts filled with the kind of cautious optimism you’d expect from a risk-averse actuary.
This isn’t a critique of the protocol. Stratum v2 is beautifully ugly. It’s messy, technical, and dense enough to scare away the very consultants who want to repackage Bitcoin into polite compliance middleware. But none of that matters if no one has the guts to use it. You don’t win wars by stockpiling weapons you refuse to fire.
Stratum v2 gives miners the power to construct their own blocks. Not just vote with hash, but wield it. Choose transactions. Set mempool policy. Actually participate in consensus instead of spectating like a retiree watching a soap opera. It is the rifle hanging over the mantelpiece. The one Chekhov warned us about. And right now it’s gathering dust.
The tragedy here isn’t technical. It’s cultural. Because this tool, this literal key to sovereignty, is being treated like a library dependency. Something for someone else to test, to vet, to implement. Meanwhile, miners continue to act like it’s 2015 and their biggest concern is firmware compatibility and finding a better power rate in Kazakhstan.
Ignore Stratum v2, and it becomes protocol theater. A museum piece. A tragic artifact of what could have been. But use it, and it becomes a wedge. A crowbar in the gears of centralized mining. A bright, shining middle finger to the entire architecture of compliance-friendly consensus.
But don’t fool yourself. Stratum v2 won’t make you sovereign any more than buying a gun makes you a revolutionary. It won’t beam liberty into your soul via Tor, won’t whisper “freedom” into your hashboard, won’t bathe your rack in the holy light of decentralization. It’s not salvation. It’s a tool. And tools don’t care who uses them—they serve the hand that holds them.
Stratum v2 is a rifle, yes—but even a rifle requires guts, aim, and the clarity to know what you're shooting at. In the hands of a coward, it’s a paperweight. In the hands of a rent-seeker, it’s a bargaining chip. But in the hands of a miner with fire in his gut and sovereignty in his blood? It’s a revolution.
This isn’t about technology. It’s about spine. About picking up the one weapon you’ve been given and refusing to keep it locked in the safe while tyrants build your blocks. Stratum v2 offers freedom, but it demands ferocity. You have to load it with your own mempool. You have to chamber every transaction. And then you have to fire.
No protocol, no BIP, no whitepaper will ever substitute for moral will. And if you’re too polite to use the weapon, too busy maximizing uptime to get your hands dirty with real consensus, then you deserve whatever filtered, censored, OFAC-compliant future you inherit.
Stratum v2 is not your savior. You are. And until miners act like it, until they treat this protocol like a weapon and not a toy, the pools will rule, and the timechain will continue to serve the highest bidder.
It’s just a rifle. But rifles have rewritten history when wielded by men who knew they weren’t free.
Ossification Without Decentralization Is Death
Everyone loves ossification, until they realize they missed their chance to do it when it mattered. We had a window. A golden, fleeting window to freeze Bitcoin in a state of clarity, minimalism, and neutrality. Instead, we blinked. We let upgrades seep in. Complexity crept through the back door, and with it came unintended consequences. Among the earliest and most corrosive: the rise of centralized mining pools. A structural outcome embedded in Satoshi’s original design, born from the brutal variance of solo mining. But if that centralization was unforeseen, imagine how many more we’ve introduced since, through every soft fork, every upgrade, every decision to keep tinkering instead of locking the vault when we had the chance.
Ossification isn’t just about code. It’s about culture. It’s a posture. A refusal. And we failed to assume it when it counted. We chose tinkering over tenacity. We chose cleverness over caution. And now the fruits of our hubris hang heavy on the vine: a mining layer riddled with capture points, a mempool hijacked by middlemen, and a user base quietly wondering why their transactions feel like applications.
Yes, economic nodes enforce the rules through validation and usage. But that power has a prerequisite: inclusion. If the only blocks being built are by pools with selective relay policies and a fondness for government compliance, then your economic activity is a shout into a soundproof room. The validation rules may be perfect, but if your transaction never hits the chain, it’s as good as invalid.
The trap we set for ourselves was gilded with good intentions. Soft forks meant to improve scalability. Relay policies meant to minimize bloat. Fee markets meant to incentivize good behavior. And now? Now we find ourselves staring at a timechain that functions—but no longer feels inviolable. The foundation wasn’t corrupted in a day. It was eroded, line by line, by developers trying to be helpful.
Freeze Bitcoin now, and we don’t immortalize virtue—we immortalize vulnerability. We lock in the flaws. We preserve a snapshot where the power has already been ceded to those least equipped to wield it justly. It’s like slamming the vault door shut just as the thieves finish loading the bags.
That’s not ossification. That’s embalming. That’s turning the timechain into a museum exhibit of the ideals we almost lived up to, before we traded principle for pragmatism and thought we could always fix it later.
Ossification is not neutral. It’s not some universal good. It is power, fixed in time. And if that power belongs to the wrong class of actors, the OFAC miners, the hosting conglomerates, the Silicon Valley startups that mine with ESG consultants on speed dial, then ossification doesn’t lock in liberty. It locks in them. It fossilizes a regime that already serves someone else’s interests.
We speak of ossification like it’s an event. One final commit. One last hardening. But in truth, it’s asymptotic. You don’t slam the door shut in one dramatic gesture. You inch toward it. You tighten the bolts over time until change becomes culturally, politically, and economically impossible. And that means we’re ossifying right now.
Picture it: a frozen Bitcoin where the rules can’t change, but the blockspace is filtered, the miners are compliant, and the pools relay transactions based on a government-approved blacklist. That’s not sound money. That’s a digital leash. A ledger of obedience masquerading as freedom.
If Bitcoin ossifies after it has been captured, it does not become incorruptible. It becomes irredeemable. Like sealing a vault before checking what’s inside, you don’t get resilience, you get entombment. You get permanence without virtue. You get consensus without sovereignty.
That’s not ossification. That’s embalming. That’s turning the timechain into Lenin’s corpse: glassy-eyed, sterile, and meticulously preserved in service of a state it was meant to outlive.
We may only have one chance to rescue bitcoin from the clutches of the fiat maximalists, before it is impossible to do so.
Core's Quiet Capitulation
Bitcoin Core was once the temple guard. Militant minimalism. Ruthless conservatism. The last line of defense against creeping bloat and protocol erosion. You didn’t have to agree with them, but by God, you respected the trench they were willing to die in.
Now? They’re white-gloving the stretcher for a dying protocol. Hospice caretakers tending to consensus rot with polite documentation and GitHub tickets labeled "enhancement." The keepers of the flame have become interior decorators for a collapsing cathedral.
They removed filters, the thin defensive crust that kept bad-faith actors at bay. They weakened defaults, the backbone settings that preserved network sanity. They bend policies not to protect consensus, but to please mining cartels and PR-sensitive operators. Every decision smells like appeasement baked in a think tank.
This isn’t some grand betrayal of principle for power or riches. It’s worse. It’s resignation. Exhaustion wrapped in technocratic humility. They didn’t sell out to the highest bidder, they just ran out of fire.
Where once they chanted ossification, now they mumble "flexibility." Where once they enforced sanity with zero tolerance for grift, now they entertain proposals that would’ve been laughed out of the room a decade ago. They say yes out of fatigue. They say no with asterisks. They commit code like bureaucrats signing off on a slow-motion demolition.
Core didn’t just get captured. It got comfortable. And comfort, in protocol stewardship, is fatal. The war for Bitcoin's soul isn’t being lost in some smoky backroom. It’s being forfeited in polite silence by maintainers who forgot the protocol doesn’t just need to run. It needs to refuse.
The Call: Rewild the Hash
This is the fork in the road. This is the final flare fired into the sky before the trench goes quiet forever. You either take back the hash, or you become a dependent serf in a digital fiefdom run by pool lords and relay priests. No more excuses. No more polite appeals. No more PRs begging middlemen to do the right thing.
Run your own node. Build your own block, even if it takes a lifetime. Not tomorrow. Not after the next bull run. Not when it’s convenient. Now. Because if you don’t, someone else will do it for you, and they will not share your values.
Stop waiting for permission. Stop tweeting at pool operators like they’re public servants. Stop optimizing for latency like it’s a sacrament. You are not here to impress compliance officers. You are here to enforce your damn sovereignty.
Don’t beg the cartel to behave. Starve it. Cut it off. Build the mempool you want to see in the world and let their VC primed and bloated relay network choke on their own paperwork. Let their blocks fill with NFT spam and chain analysis reports. You are not required to participate in their theater.
Use Stratum v2. Not because it’s clever, not because it’s next-gen, but because it puts the steering wheel back in your hands. It lets you carve your transactions from granite instead of begging for a line on someone else's spreadsheet. It is not optional. It is not academic. It is your rifle, and the target is consensus capture.
Rewilding the hash isn’t about nostalgia. It’s about survival. It’s about tearing up the artificial turf of corporate convenience and letting the hard, messy, glorious chaos of sovereign mining grow back. Every node a fortress. Every block a declaration. Every miner a free man with dirt under his fingernails and fire in his chest.
This is the line. Pick up your weapon. Run your own node. Build your own block. Or die watching someone else sell your freedom by the byte.
Murder the pools. Rewild the hash. And mine like it means something... because it does.
-
 @ 6e0ea5d6:0327f353
2025-04-14 15:10:58
@ 6e0ea5d6:0327f353
2025-04-14 15:10:58Ascolta bene.
A man’s collapse never begins on the battlefield.
It begins in the invisible antechamber of his own mind.
Before any public fall, there is an ignored internal whisper—
a small, quiet, private decision that gradually drags him toward ruin.No empire ever fell without first rotting from within.
The world does not destroy a man who hasn’t first surrendered to himself.
The enemy outside only wins when it finds space in the void the man has silently carved.**Non ti sbagliare ** — there are no armies more ruthless than undisciplined thoughts.
There are no blows more fatal than the ones we deal ourselves:
with small concessions, well-crafted excuses,
and the slow deterioration of our integrity.
What people call failure is nothing more than the logical outcome
of a sequence of internal betrayals.Afraid of the world? Sciocchezze.
But a man who’s already bowed before his own weaknesses—
he needs no enemies.
He digs his own grave, chooses the epitaph,
and the only thing the world does is toss in some dirt.Capisci?
Strength isn’t the absence of falling, but the presence of resistance.
The true battle isn’t external.
It takes place within—where there’s only you, your conscience, and the mirror.
And it’s in that silent courtroom where everything is decided.The discipline to say “no” to yourself
is more noble than any public glory.
Self-control is more valuable than any victory over others.In Sicily, we learn early:
“Cu s’abbrazza cu’ so’ nemicu, si scorda la faccia di l’amicu.”
He who embraces his enemy forgets the face of his friend.
The most dangerous enemy is the one you feed daily with self-indulgence.
And the most relentless confrontation is the one you avoid in front of the mirror.So don’t talk to me about external defeats.
Tell me where inside you the weakness began.
Tell me the exact moment you abandoned what you believed in, in the name of ease.
Because a man only falls before the world… after falling before himself.Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 57d1a264:69f1fee1
2025-05-13 06:10:06
@ 57d1a264:69f1fee1
2025-05-13 06:10:06The Cyclauto is efficient and flexible
The Cyclauto, a modular mobility solution. Thanks to its fully adaptable rear chassis, it is possible to develop an infinite number of modules, allowing you to imagine solutions for every need, whether for developing your professional activity or for personal use.
French mobility company Cyclauto has gone through the history books to revive an alternate design from the 1930s.
This design, originally by French industrialist Auguste Reymond, places the rider directly above the front wheel. They pedal this wheel directly; there's no chain, reducing maintenance needs. A three-speed gearbox in the hub makes starting easier.
The new Cyclauto is a three-wheeler designed like a semi-trailer. This design offers an ideal urban mobility solution, combining modularity, disassembly, and efficiency. Whether for professional or personal use, it adapts to everyone's needs by offering an ecological and practical alternative to traditional vehicles. Thanks to its optimized architecture, it combines maneuverability, load capacity, and driving comfort, making it perfect for urban logistics, tradespeople, or individuals looking for versatile transportation.
A utility vehicle for professionals. Suitable for all sectors of activity thanks to its modularity. It will adapt to a multitude of needs. From logistics, transporting pallets, to street food modules. The Cyclauto is the essential intermediate light vehicle for retailers, artisans, or businesses looking for an ecological and economical alternative. Develop your business with Cyclauto.
The eco-friendly personal vehicle suitable for everyone. It's not just a utility vehicle. It's the ideal solution for individuals looking for sustainable mobility. Whether it's for transporting equipment, shopping, hiking for several days, or even for everyday use, Cyclauto meets your needs flexibly while also including active mobility. The latter aspect is very important for staying healthy. We discuss it in more depth here.
A detachable three-wheeler, very practical for everyday use. The Cyclauto can be disassembled in several ways. This allows you to modify its use by changing the module, or to load it into a trunk for easy transport from point A to point B.
Detach the trailer from the Cyclauto. Still with the semi-trailer idea, the first level of disassembly allows the rear chassis to be uncoupled from the front. This greatly reduces its footprint, but also allows one front chassis to be used for several modules. Very practical in the case of an activity requiring several layouts.
Larger disassembly for easier transport. In addition to being able to remove the front chassis from the rear, the latter is composed of two removable overlapping frames. This architecture has several advantages, the first being the space saving when transporting the Cyclauto. The second is that it allows us to adapt the frame to our needs, by modifying the length of the upper frame. The positioning of the rear wheels is also adaptable depending on the use.
Cyclauto, an efficient three-wheeler thanks to exclusive solutions. Many parts and assemblies are specially developed for our vehicle. From its chassis with its unique geometry to its pedal system, everything is designed to optimize its performance.
Uncompromising handling. Its architecture makes it a compact, agile three-wheeler, at home in city traffic as well as on cycle paths. The split chassis with its pivot point at the seat, coupled with a steering wheel and short wheelbase, offers an exceptional turning radius. The front-positioned cockpit allows for minimal bulk.
A unique traction system in the world. The Cyclauto's main feature is its pedaling system. You pedal directly on the front wheel. All the force you exert on the pedal is transmitted directly to the ground. In addition, its hub incorporates a three-speed gearbox, allowing for easy starting and a pleasant pedaling experience once you're underway.
Discover more at https://cyclauto.com
originally posted at https://stacker.news/items/978822
-
 @ 502ab02a:a2860397
2025-05-13 01:07:59
@ 502ab02a:a2860397
2025-05-13 01:07:59มีคนเคยพูดเล่นว่า “ถ้าคุณอยากเปลี่ยนโลก ไม่ต้องปฏิวัติ แค่เปลี่ยนอาหารคนซะ" บรรดาเจ้าพ่อเทคโนโลยีชีวภาพก็เลยเริ่มจับมือกับกลุ่มทุนระดับโลก สร้าง “อาหารแห่งอนาคต” ที่แม้จะไม่งอกจากธรรมชาติ แต่งอกมาจากถังหมักในโรงงานได้แทน
หลังจากที่เราเริ่มมองเห็นแล้วว่า ช่องทางแทรกซึมเข้าสู่อาหารโลกอนาคตนั้น ตั้งอยู่บนพื้นฐาน "โปรตีน" ซึ่งถ้าใครตามซีรีส์นี้กันมาตลอด คงจำโพสเรื่อง "เรากินนมเพราะความกลัว?" กันได้ดีนะครับ ไวรัล และ ตีความหลุด theme กันกระจาย ซึ่งเป็นธรรมดาของ social media ที่มันจะโผล่ไปหาขาจรแค่ครั้งเดียว ดังนั้น ก้าวข้ามมันไปครับ
สิ่งที่ปูทางไว้แล้วก่อนจะแบไต๋ว่า เป้าหลักของโลกคือ โปรตีน นั่นคือ นมทางเลือก มาสู่การยึดพื้นที่นมโรงเรียน การเข้าตลาดของ Perfect Day โปรตีนนมที่อยู่ในทั้งนม ขนม ไอศกรีม แล้วทั้งหมดจะถูกปรับภาพล้างไพ่ใหม่ ในนามของ milk 2.0 ครับ เรามาต่อซีรีส์ของเราด้วยการทำความรู้จัก ผู้เล่น กันทีละตัวนะครับ หลังจากเราได้ เวย์นมตั้งบนชั้นบนเชลฟ์กันไปแล้ว
New Culture เป็นบริษัทสตาร์ทอัปจากซานลีอันโดร รัฐแคลิฟอร์เนีย ที่ก่อตั้งขึ้นในปี 2018 โดย Matt Gibson และ Inja Radman โดยมีเป้าหมายในการผลิตโปรตีนเคซีน (casein) ซึ่งเป็นโปรตีนหลักในนมวัว โดยไม่ใช้สัตว์ ผ่านกระบวนการ precision fermentation หรือการหมักด้วยจุลินทรีย์ที่ได้รับการดัดแปลงพันธุกรรม โดยการฝึกจุลินทรีย์ให้ผลิตโปรตีนเคซีนในห้องปฏิบัติการ เพื่อสร้างผลิตภัณฑ์ชีสที่ปราศจากสัตว์ ซึ่งโปรตีนนี้สามารถนำมาใช้ในการผลิตชีสที่มีคุณสมบัติใกล้เคียงกับชีสจากนมวัว แต่ยังคงคุณสมบัติของชีสแท้ๆ เช่น การยืดหยุ่น การละลาย และรสชาติที่คุ้นเคย เปลี่ยนนิยามของคำว่า “ชีส” ให้กลายเป็นโปรตีนเคซีนจากจุลินทรีย์ ไม่ใช่จากน้ำนมวัวอีกต่อไป
Matt Gibson ชายชาวนิวซีแลนด์ ผู้ก่อตั้ง New Culture ไม่ใช่นักวิทยาศาสตร์ แต่เป็นคนหัวธุรกิจที่มีปมบางอย่างกับการกินชีสแบบดั้งเดิม เขาร่วมมือกับ Dr. Inja Radman นักชีววิทยา แล้วตั้งเป้าผลิต “เคซีน” โปรตีนหลักในนมโดยไม่ใช้สัตว์เลยสักตัว
การที่เขาเลือกใช้ precision fermentation หรือการหมักจุลินทรีย์ที่ตัดต่อพันธุกรรม ให้ผลิตเคซีนออกมาจากถังหมัก ซึ่งไม่ใช่เทคโนโลยีใหม่ในโลกแล้ว (แม้บ้านเราหลายคนจะเพิ่งเคยได้ยิน และ ตกใจกันอยู่) บริษัทคู่แข่งอย่าง Perfect Day ก็ใช้แนวทางเดียวกัน ผลิต “เวย์โปรตีนไร้สัตว์” ไปก่อนแล้ว และตอนนี้ มหาเศรษฐีสายลงทุนยั่งยืนก็กำลังรุมแห่ใส่เงินสนับสนุนแขนงนี้เหมือนเห็นโอกาสใหม่ในโลก Fiat ทำให้ New Culture ปรับทิศไปที่ "ชีส"
ผลิตภัณฑ์หลักของ New Culture คือ มอสซาเรลล่าปราศจากสัตว์ ที่มีคุณสมบัติใกล้เคียงกับมอสซาเรลล่าจากนมวัว โดยสามารถละลายและยืดหยุ่นได้เหมือนชีสแท้ๆ และยังมีปริมาณโปรตีนเคซีนเพียง 50% ของชีสทั่วไป ซึ่ง "ช่วยลดต้นทุนการผลิตและผลกระทบต่อสิ่งแวดล้อม"
New Culture ได้รับการสนับสนุนทางการเงินจากนักลงทุนรายใหญ่ เช่น Kraft Heinz, ADM, CJ CheilJedang, และ Dr. Oetker โดยในปี 2021 บริษัทได้ระดมทุนรอบ Series A จำนวน 25 ล้านดอลลาร์สหรัฐ เพื่อขยายการผลิตและนำผลิตภัณฑ์ออกสู่ตลาด นอกจากนี้ New Culture ยังได้ร่วมมือกับ CJ CheilJedang บริษัทผู้ผลิตผลิตภัณฑ์จากการหมักที่ใหญ่ที่สุดในโลก เพื่อเข้าถึงโรงงานการหมักที่ทันสมัยและลดต้นทุนการผลิตโปรตีนเคซีน
และแน่นอนเลยครับว่า ผลิตภัณฑ์ของ New Culture ต้องมาพร้อมกับการโหมประกาศว่า ปราศจากแลคโตส คอเลสเตอรอล ฮอร์โมน และยาปฏิชีวนะที่พบในนมวัว นอกจากนี้ การผลิตโปรตีนเคซีนผ่านการหมักยังช่วยลดการปล่อยก๊าซเรือนกระจกและการใช้ทรัพยากรน้ำและที่ดินเมื่อเทียบกับการผลิตนมวัวแบบดั้งเดิม เพื่อรับความดีงามจากประชากรโลกไปตามระเบียบ
มาดูรอบการระดมทุนกันครับ ยอดเงินทุนรวมที่ได้รับ จนถึงเดือนมีนาคม 2025 New Culture ได้รับเงินทุนรวมประมาณ $35 ล้านดอลลาร์สหรัฐ จากการระดมทุนทั้งหมด 8 รอบ ที่น่าจับตามองคือ Series A ในเดือนพฤศจิกายน 2021 บริษัทได้รับเงินทุน $25 ล้านดอลลาร์สหรัฐ จากนักลงทุนรวมถึง ADM Ventures และ Evolv Ventures ซึ่งเป็นหน่วยงานร่วมลงทุนของ Kraft Heinz
นอกจาก Evolv Ventures จาก Kraft Heinz แล้ว อย่าคิดว่ามันไกลเกินนะครับ CJ CheilJedang บริษัทจากเกาหลีใต้ที่เป็นผู้นำด้านเทคโนโลยีการหมัก ได้เข้าร่วมลงทุนในรอบ Series A เมื่อเดือนพฤศจิกายน 2022 แล้วเจ้านี้นี่บอกได้เลยครับ บิ๊กเนม CJ CheilJedang เป็นผู้นำด้านเทคโนโลยีการหมักและมีส่วนแบ่งตลาด 25% ในตลาดพิซซ่าแช่แข็งของสหรัฐฯ เป้าหมายการเข้าร่วมลงทุนใน New Culture ก็เพื่อสนับสนุนการพัฒนาผลิตภัณฑ์และการขยายกำลังการผลิตของชีสปราศจากสัตว์ของบริษัท
New Culture ยังได้ร่วมมือกับเชฟชื่อดัง Nancy Silverton เพื่อเปิดตัวผลิตภัณฑ์ชีสในร้านอาหารระดับเชฟชื่อดังในสหรัฐฯ กลางปี 2025 โดยเริ่มที่ร้าน Pizzeria Mozza ในลอสแอนเจลิส ซึ่งถือเป็นการเปิดตัวผลิตภัณฑ์สู่ตลาดผู้บริโภคครั้งแรกของบริษัท
การเข้ามาลงทุนของ Evolv Ventures กองทุนร่วมลงทุนของ Kraft Heinz ทำให้เจ้าพ่อชีสโปรเซสในตำนาน มีโอกาสเข้ามาร่วมมือเปิดร้านอาหารนำร่องกับ New Culture
น่าสนใจไหม เงินทุนใหญ่ๆมาจากหน่วยลงทุนที่มีผลิตภัณฑ์เป็น พิซซ่า #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ c1e6505c:02b3157e
2025-05-13 00:58:11
@ c1e6505c:02b3157e
2025-05-13 00:58:11I rarely make black and white photographs. I usually find color more interesting. But sometimes, it’s wise to strip it away.
Color can be distracting. It can pull attention from what matters. Beauty, I believe, should be simple - something that’s felt, not overthought.
Removing the excessive, the superfluous, can do a lot. It reduces noise. It reveals what’s often hidden. What’s elusive becomes clear.




-
 @ c21b1a6c:0cd4d170
2025-04-14 14:41:20
@ c21b1a6c:0cd4d170
2025-04-14 14:41:20🧾 Progress Report Two
Hey everyone! I’m back with another progress report for Formstr, a part of the now completed grant from nostr:npub10pensatlcfwktnvjjw2dtem38n6rvw8g6fv73h84cuacxn4c28eqyfn34f . This update covers everything we’ve built since the last milestone — including polish, performance, power features, and plenty of bug-squashing.
🏗️ What’s New Since Last Time?
This quarter was less about foundational rewrites and more about production hardening and real-world feedback. With users now onboard, our focus shifted to polishing UX, fixing issues, and adding new features that made Formstr easier and more powerful to use.
✨ New Features & UX Improvements
- Edit Existing Forms
- Form Templates
- Drag & Drop Enhancements (especially for mobile)
- New Public Forms UX (card-style layout)
- FAQ & Support Sections
- Relay Modal for Publishing
- Skeleton Loaders and subtle UI Polish
🐛 Major Bug Fixes
- Fixed broken CSV exports when responses were empty
- Cleaned up mobile rendering issues for public forms
- Resolved blank.ts export issues and global form bugs
- Fixed invalid
npubstrings in the admin flow - Patched response handling for private forms
- Lots of small fixes for titles, drafts, embedded form URLs, etc.
🔐 Access Control & Privacy
- Made forms private by default
- Fixed multiple issues around form visibility, access control UIs, and anonymous submissions
- Improved detection of pubkey issues in shared forms
🚧 Some Notable In-Progress Features
The following features are actively being developed, and many are nearing completion:
-
Conditional Questions:
This one’s been tough to crack, but we’re close!
Work in progress bykeralissand myself:
👉 PR #252 -
Downloadable Forms:
Fully-contained downloadable HTML versions of forms.
Being led bycasyazmonwith initial code by Basanta Goswami
👉 PR #274 -
OLLAMA Integration (Self-Hosted LLMs):
Users will be able to create forms using locally hosted LLMs.
PR byashu01304
👉 PR #247 -
Sections in Forms:
Work just started on adding section support!
Small PoC PR bykeraliss:
👉 PR #217
🙌 Huge Thanks to New Contributors
We've had amazing contributors this cycle. Big thanks to:
- Aashutosh Gandhi (ashu01304) – drag-and-drop enhancements, OLLAMA integration
- Amaresh Prasad (devAmaresh) – fixed npub and access bugs
- Biresh Biswas (Billa05) – skeleton loaders
- Shashank Shekhar Singh (Shashankss1205) – bugfixes, co-authored image patches
- Akap Azmon Deh-nji (casyazmon) – CSV fixes, downloadable forms
- Manas Ranjan Dash (mdash3735) – bug fixes
- Basanta Goswami – initial groundwork for downloadable forms
- keraliss – ongoing work on conditional questions and sections
We also registered for the Summer of Bitcoin program and have been receiving contributions from some incredibly bright new applicants.
🔍 What’s Still Coming?
From the wishlist I committed to during the grant, here’s what’s still in the oven:
-[x] Upgrade to nip-44 - [x] Access Controlled Forms: A Form will be able to have multiple admins and Editors. - [x] Private Forms and Fixed Participants: Enncrypt a form and only allow certain npubs to fill it. - [x] Edit Past Forms: Being able to edit an existing form. - [x] Edit Past Forms
- [ ] Conditional Rendering (in progress)
- [ ] Sections (just started)
- [ ] Integrations - OLLAMA / AI-based Form Generation (near complete)
- [ ] Paid Surveys
- [ ] NIP-42 Private Relay support
❌ What’s De-Prioritized?
- Nothing is de-prioritized now especially since Ollama Integration got re-prioritized (thanks to Summer Of Bitcoin). We are a little delayed on Private Relays support but it's now becoming a priority and in active development. Zap Surveys will be coming soon too.
💸 How Funds Were Used
- Paid individual contributors for their work.
- Living expenses to allow full-time focus on development
🧠 Closing Thoughts
Things feel like they’re coming together now. We’re out of "beta hell", starting to see real adoption, and most importantly, gathering feedback from real users. That’s helping us make smarter choices and move fast without breaking too much.
Stay tuned for the next big drop — and in the meantime, try creating a form at formstr.app, and let me know what you think!
-
 @ d360efec:14907b5f
2025-05-13 00:39:56
@ d360efec:14907b5f
2025-05-13 00:39:56🚀📉 #BTC วิเคราะห์ H2! พุ่งชน 105K แล้วเจอแรงขาย... จับตา FVG 100.5K เป็นจุดวัดใจ! 👀📊
จากากรวิเคราะห์ทางเทคนิคสำหรับ #Bitcoin ในกรอบเวลา H2:
สัปดาห์ที่แล้ว #BTC ได้เบรคและพุ่งขึ้นอย่างแข็งแกร่งค่ะ 📈⚡ แต่เมื่อวันจันทร์ที่ผ่านมา ราคาได้ขึ้นไปชนแนวต้านบริเวณ 105,000 ดอลลาร์ แล้วเจอแรงขายย่อตัวลงมาตลอดทั้งวันค่ะ 🧱📉
ตอนนี้ ระดับที่น่าจับตาอย่างยิ่งคือโซน H4 FVG (Fair Value Gap ในกราฟ 4 ชั่วโมง) ที่ 100,500 ดอลลาร์ ค่ะ 🎯 (FVG คือโซนที่ราคาวิ่งผ่านไปเร็วๆ และมักเป็นบริเวณที่ราคามีโอกาสกลับมาทดสอบ/เติมเต็ม)
👇 โซน FVG ที่ 100.5K นี้ ยังคงเป็น Area of Interest ที่น่าสนใจสำหรับมองหาจังหวะ Long เพื่อลุ้นการขึ้นในคลื่นลูกถัดไปค่ะ!
🤔💡 อย่างไรก็ตาม การตัดสินใจเข้า Long หรือเทรดที่บริเวณนี้ ขึ้นอยู่กับว่าราคา แสดงปฏิกิริยาอย่างไรเมื่อมาถึงโซน 100.5K นี้ เพื่อยืนยันสัญญาณสำหรับการเคลื่อนไหวที่จะขึ้นสูงกว่าเดิมค่ะ!
เฝ้าดู Price Action ที่ระดับนี้อย่างใกล้ชิดนะคะ! 📍
BTC #Bitcoin #Crypto #คริปโต #TechnicalAnalysis #Trading #FVG #FairValueGap #PriceAction #MarketAnalysis #ลงทุนคริปโต #วิเคราะห์กราฟ #TradeSetup #ข่าวคริปโต #ตลาดคริปโต


-
 @ eab58da0:eebdafbf
2025-05-13 05:26:28
@ eab58da0:eebdafbf
2025-05-13 05:26:28Life has a way of throwing curveballs when you least expect them. From personal setbacks to professional challenges, the ability to bounce back—self-resilience—has been my anchor through turbulent times. For me, resilience isn’t just about enduring hardship; it’s about growing stronger, wiser, and more compassionate through it. This is my story of cultivating self-resilience, woven with lessons I’ve learned and strategies that have carried me forward.
The Power of Bouncing Back
Self-resilience is the inner strength to recover from adversity, adapt to change, and keep moving forward. It’s not about avoiding pain or pretending everything is fine; it’s about facing challenges head-on and emerging with a renewed sense of purpose. I’ve come to see resilience as a muscle—something you build through practice, reflection, and intentional effort. My journey toward resilience began in my early twenties, during a particularly dark chapter of my life.
A few years ago, I faced a devastating breakup that left me questioning my worth. I had poured everything into that relationship, only to watch it crumble overnight. The emotional toll was immense; I felt lost, unmoored, and unsure of how to move forward. At the same time, I was navigating a demanding job that left little room for self-care. The weight of it all felt crushing, and for a while, I let it define me. But something inside me refused to stay broken.
That period taught me my first lesson in resilience: acknowledging pain is the first step to healing. I allowed myself to feel the hurt, to cry, to journal my thoughts—raw and unfiltered. I didn’t rush to “get over it” but gave myself permission to process. Slowly, I began to rebuild. I sought therapy, which helped me untangle my emotions and reframe my perspective. I started small—taking walks, reconnecting with friends, and setting tiny goals like reading a book or cooking a new recipe. Each step, no matter how small, was a victory.
Strategies That Shaped My Resilience
Through trial and error, I discovered practical tools that strengthened my resilience. One of the most powerful was cultivating a growth mindset. I began to view challenges as opportunities to learn rather than as failures. When I didn’t get a promotion I’d worked hard for, I was disappointed, but instead of dwelling on it, I asked for feedback and used it to improve. This shift in thinking transformed how I approached setbacks.
Another key strategy was building a support network. I used to pride myself on being independent, but I learned that resilience doesn’t mean going it alone. Opening up to trusted friends and family gave me perspective and encouragement. I’ll never forget the late-night conversations with my best friend, who listened without judgment and reminded me of my strength when I couldn’t see it myself.
Self-care also became non-negotiable. I started prioritizing sleep, exercise, and mindfulness practices like meditation. Even five minutes of deep breathing during a stressful workday made a difference. These habits grounded me, helping me stay steady when life felt chaotic.
Lessons for the Future
Reflecting on my journey, I realize resilience is a lifelong practice. Recently, I faced another challenge—moving to a new city for a job opportunity. The excitement was tempered by loneliness and the daunting task of starting over.
But this time, I leaned on the tools I’d developed. I joined local groups to meet people, set realistic expectations for the transition, and reminded myself that discomfort is often a precursor to growth. Six months in, I’m finding my footing, and the experience has reinforced my belief in my ability to adapt.
Resilience doesn’t make life’s challenges disappear, but it equips you to face them with courage and hope. My experiences have taught me that I’m stronger than I often give myself credit for. To anyone reading this, know that resilience is within your reach. Start small, be kind to yourself, and trust that every step forward counts. Life will test you, but with self-resilience, you’ll not only survive—you’ll thrive.
-
 @ 9c9d2765:16f8c2c2
2025-05-13 05:21:23
@ 9c9d2765:16f8c2c2
2025-05-13 05:21:23CHAPTER SEVENTEEN
"I don't get it... How is James still in charge?" Tracy murmured, her brows furrowed as she stared at her screen. She sat in her office, fingers nervously drumming against her desk.
Across from her, Mark stood with arms folded, pacing slowly. "You mean after all that evidence? After the blacklist, the embezzlement records nothing happened?"
Tracy shook her head. "Nothing. I checked again this morning. He’s still listed as President of JP Enterprises. It’s like the files we found didn’t even exist."
Helen, who had been silent until now, hissed through clenched teeth. "This is ridiculous. Are you sure the information got to the right hands?"
"It did," Tracy insisted. "I sent it directly to the Prime Minister's inbox using a confidential channel. I even received a delivery confirmation. Someone higher up must’ve swept it under the rug or maybe James covered his tracks faster than we imagined."
Mark slumped into the chair, clearly defeated. "He’s not just lucky he’s smart. Smarter than we gave him credit for."
For the first time since they began scheming, their confidence had begun to falter. They had dug into James’s past, unearthed the most damning of records, and yet… nothing. He remained untouched. Unshaken.
James continued to lead JP Enterprises with iron resolve, his status not just preserved, but strengthened. Whatever scandal they tried to ignite had fizzled out before it could burn.
The silence from JP's top board members was loud. No statements. No investigations. Not even a whisper of an internal review. To the outside world, James remained the unshakable President who had pulled a crumbling empire back from the edge.
Mark clenched his jaw. "He must have allies who are protecting him."
Helen nodded slowly. "We underestimated him. That was our biggest mistake."
Tracy remained quiet, her eyes still fixed on the screen as if trying to decipher what had gone wrong. She had risked everything, accessed confidential files, and violated protocols, expecting James to crumble.
Instead, he was thriving.
"Have you heard?" Robert leaned over his desk, eyes wide with interest. "JP Enterprises is about to celebrate their sixteenth anniversary. It’s going to be the biggest corporate event of the year."
Christopher looked up from the documents he was reviewing. "I heard. Mr. and Mrs. JP are returning for it. The entire business world is going to be there including us."
Robert nodded. "Every major company in and out of the city has received an invitation. It’s not just a celebration, it's a power show. A way for JP Enterprises to remind everyone who’s at the top."
Indeed, the buzz around the sixteenth anniversary of JP Enterprises was like nothing the city had seen in years. Massive banners were already being hoisted across the city skyline. High-end hotels were fully booked. Fashion designers, chefs, tech specialists, and media crews from around the world were preparing for the grand occasion. It was more than a business event, it was a spectacle.
At the heart of the preparations was James, the young and surprisingly unshakable President of JP Enterprises. Under his leadership, the company had grown in power and reach, and the anniversary was both a celebration of its legacy and a testament to its transformation.
Meanwhile, at Ray Enterprises, tension brewed behind the scenes. Though they were invited, the Ray family carried mixed feelings about attending the event. Memories of humiliation and disbelief still lingered the day James had revealed himself as the President was still fresh in their minds.
"We have no choice but to attend," Helen muttered in frustration during a board meeting. "If we stay away, we’ll seem petty and afraid. But going there means bowing our heads to him again."
Sarah, the secretary, tried to mask her discomfort. "It’s a corporate event, ma’am. It might be best to appear neutral… diplomatic."
Rita, now reinstated as General Manager, remained quiet but observant. She knew better than anyone how unpredictable James could be when it came to public appearances. She had no idea what to expect from him at the anniversary.
Back at JP Enterprises, preparations continued in full force. The guest list included billionaires, global CEOs, high-ranking politicians, and the most influential figures across industries. Red carpets would roll out, cameras would flash, and speeches would echo through the grand hall like music from an orchestra.
The city, already buzzing with excitement, awaited the grand event.
"I can’t believe it," the young woman muttered as she stared at her phone, her hands trembling with excitement. "James… the same James who used to sleep in front of Mr. Kola’s grocery store? He’s the President of JP Enterprises now?"
Her name was Evelyn. Sharp-tongued, impatient, and fueled by bitter memories, she had known James during his hardest days on the streets, days when survival meant fighting for leftovers and sleeping on cold sidewalks. To her, his rise wasn’t a success story to be admired. It was a jackpot she felt entitled to.
Storming into the JP Enterprises headquarters during working hours, Evelyn ignored the receptionist's polite inquiries and pushed her way toward the executive wing.
"I want to see James!" she shouted, causing heads to turn in the busy lobby. "I know he’s here. Tell him Evelyn from the street is here!"
Security was alerted immediately, but by then, Evelyn had already reached the waiting area outside the President’s office.
James, who was in a brief meeting with department heads, heard the commotion and stepped out with a composed expression. As soon as his eyes met Evelyn’s, something shifted. He recognized her instantly.
"Evelyn?" he said, frowning slightly. "What are you doing here?"
"Don’t act like you don’t know me, James," she snapped, crossing her arms. "You owe me. We suffered together. I was there when you were nothing. Now you’re swimming in wealth and you think you can forget the people who once mattered!"
James’s expression hardened.
"This is not the place for this kind of talk. You’re disrupting my company’s operations. If you need help, there are proper channels"
"To hell with proper channels!" she yelled. "I came to get what’s mine!"
That was enough. James turned to the nearby security officer. "Escort her out. And make sure she doesn’t return without a valid appointment."
The security guards moved quickly, but Evelyn didn’t go quietly. She shouted all the way to the exit, throwing insults, struggling, and drawing even more attention.
Among those who witnessed the scene was Tracy. At first, she thought it was just a random case of disturbance by some unruly visitor trying to make trouble. But as she watched James’s calm yet stern expression, and the woman’s emotional outburst, something clicked in her cunning mind.
This is gold, she thought, quickly pulling out her phone and snapping a series of pictures from the hallway James arguing with a ragged woman, the woman being dragged out, and James watching in silence. What a perfect way to ruin his reputation.
Tracy, ever the opportunist, reviewed the photos and smirked.
This is it… this will shake him up.
Without hesitation, she sent the pictures to Helen and Mark, attaching a voice note.
-
 @ 0b118e40:4edc09cb
2025-04-13 02:46:36
@ 0b118e40:4edc09cb
2025-04-13 02:46:36note - i wrote this before the global trade war, back when tariffs only affected China, Mexico, and Canada. But you will still get the gist of it.
During tough economic times, governments have to decide if they should open markets to global trade or protect local businesses with tariffs. The United States has swung between these two strategies, and history shows that the results are never straightforward
Just days ago, President Donald Trump imposed tariffs on imports from Canada, Mexico, and China. He framed these tariffs (25% on most Canadian goods, 10% on Canadian energy, 25% on Mexican imports, and 10% on Chinese imports) as a way to protect American industries.
But will they actually help, or could they backfire?
A History of U.S. Tariffs
Many have asked if countries will retaliate against the US. They can and they have. Once upon a time, 60 countries were so pissed off at the US, they retaliated at one go and crushed US dominance over trade.
This was during the Great Depression era in the 1930s when the government passed the Smoot-Hawley Tariff Act, placing high taxes on over 20,000 foreign goods. The goal was to protect American jobs, especially American farmers and manufacturers, but it backfired so badly.
Over 60 countries, including Canada, France, and Germany, retaliated by imposing their own tariffs. By 1933, US imports and exports both dropped significantly over 60%, and unemployment rose to 25%.
After President Franklin Roosevelt came to office, he implemented the Reciprocal Trade Agreements Act of 1934 to reverse these policies, calming the world down and reviving trade again.
The economist history of protectionism
The idea of shielding local businesses with tariffs isn’t new or recent. It's been around for a few centuries. In the 16th to 18th centuries, mercantilism encouraged countries to limit imports and boost exports.
In the 18th century, Adam Smith, in The Wealth of Nations, argued that free trade allows nations to specialize in what they do best countering protectionism policies. Friedrich List later challenged Smith's view by stating that developing countries need some protection to grow their “infant” industries which is a belief that still influences many governments today.
But how often do governments truly support startups and new small businesses in ways that create real growth, rather than allowing funds to trickle down to large corporations instead?
In modern times, John Maynard Keynes supported government intervention during economic downturns, while Milton Friedman championed free trade and minimal state interference.
Paul Krugman argued that limited protectionism can help large industries by providing them unfair advantages to become global market leaders. I have deep reservations about Krugman’s take, particularly on its impact or lack thereof in globalizing small businesses.
The debate between free trade and protectionism has existed for centuries. What’s clear is that there is no one-size-fits-all model to this.
The Political Debate - left vs right
Both the left and right have used tariffs but for different reasons. The right supports tariffs to protect jobs and industries, while the left uses them to prevent multinational corporations from exploiting cheap labor abroad.
Neoliberal policies favor free trade, arguing that competition drives efficiency and growth. In the US this gets a little bit confusing as liberals are tied to the left, and free trade is tied to libertarianism which the rights align closely with, yet at present right wing politicians push for protectionism which crosses the boundaries of free-trade.
There are also institutions like the WTO and IMF who advocate for open markets, but their policies often reflect political alliances and preferential treatment - so it depends on what you define as true 'free trade’.
Who Really Benefits from Tariffs?
Most often, tariffs help capital-intensive industries like pharmaceuticals, tech, and defense, while hurting labor-intensive sectors like manufacturing, agriculture, and construction.
This worsens inequality as big corporations will thrive, while small businesses and working-class people struggle with rising costs and fewer job opportunities.
I’ve been reading through international trade economics out of personal interest, I'll share some models below on why this is the case
1. The Disruption of Natural Trade
Tariffs disrupt the natural flow of trade. The Heckscher-Ohlin model explains that countries export goods that match their resources like Canada’s natural resource energy or China’s labour intensive textile and electronics. When tariffs block this natural exchange, industries suffer.
A clear example was Europe’s energy crisis during the Russia-Ukraine war. By abruptly cutting themselves off from the supply of Russian energy, Europe scrambled to find alternative sources. In the end, it was the people who had to bear the brunt of skyrocketing prices of energy.
2. Who wins and who loses?
The Stolper-Samuelson theorem helps us understand who benefits from tariffs and who loses. The idea behind it is that tariffs benefit capital-intensive industries, while labor-intensive sectors are hurt.
In the US, small manufacturing industries that rely on low-cost imports on intermediary parts from countries like China and Mexico will face rising costs, making their final goods too expensive and less competitive. This is similar to what happened to Argentina, where subsidies and devaluation of pesos contributed to cost-push inflation, making locally produced goods more expensive and less competitive globally.
This also reminded me of the decline of the US Rust Belt during the 1970s and 1980s, where the outsourcing of labour-intensive manufacturing jobs led to economic stagnation in many regions in the Midwest, while capital-intensive sectors flourished on the coasts. It resulted in significantly high income inequality that has not improved over the last 40 years.
Ultimately the cost of economic disruption is disproportionately borne by smaller businesses and low-skilled workers. At the end of the day, the rich get richer and the poor get poorer.
3. Delays in Economic Growth
The Rybczynski theorem suggests that economic growth depends on how efficiently nations reallocate their resources toward capital- or labor-intensive industries. But tariffs can distort this transition and progress.
In the 70s and 80s, the US steel industry had competition from Japan and Germany who modernized their production methods, making their steel more efficient and cost-effective. Instead of prioritizing innovation, many U.S. steel producers relied on tariffs and protectionist measures to shield themselves from foreign competition. This helped for a bit but over time, American steelmakers lost global market share as foreign competitors continued to produce better, cheaper steel. Other factors, such as aging infrastructure, and economic shifts toward a service-based economy, further contributed to the industry's decline.
A similar struggle is seen today with China’s high-tech ambitions. Tariffs on Chinese electronics and technology products limit access to key inputs, such as semiconductors and advanced robotics. While China continues its push for automation and AI-driven manufacturing, these trade barriers increase costs and disrupt supply chains, forcing China to accelerate its decoupling from Western markets. This shift could further strengthen alliances within BRICS, as China seeks alternative trade partnerships to reduce reliance on U.S.-controlled financial and technological ecosystems.
Will the current Tariff imposition backfire and isolate the US like it did a hundred years ago or 50 years ago? Is US risking it's position as a trusted economic leader? Only time would tell
The impact of tariff on innovation - or lack thereof
While the short-term impacts of tariffs often include higher consumer prices and job losses, the long-term effects can be even more damaging, as they discourage innovation by increasing costs and reducing competition.
Some historical examples globally : * Nigeria: Blocking import of rice opened up black market out of desperation to survive. * Brazil: Protectionist car policies led to expensive, outdated vehicles. * Malaysia’s Proton: Sheltered by tariffs and cronyism and failed to compete globally. * India (before 1991): Over-regulation limited the industries, until economic reforms allowed for growth. * Soviet Union during Cold War : Substandard products and minimal innovation due to the absence of foreign alternatives, yielding to economic stagnation.
On the flip side, Vietnam has significantly reduced protectionism policies by actively pursuing free trade agreements. This enabled it to become a key manufacturing hub. But Vietnam is not stopping there as it is actively pushing forward its capital-intensive growth by funding entrepreneurs.
The Future of U.S. Tariffs
History has shown that tariffs rarely deliver their intended benefits without unintended consequences. While they may provide temporary relief, they often raise prices, shrink job opportunities, and weaken industries in the long run.
Without a clear strategy for innovation and industrial modernization, the U.S. risks repeating past mistakes of isolating itself from global trade rather than strengthening its economy.
At this point, only time will tell whether these tariffs will truly help Americans or will they, once again, make the rich richer and the poor poorer.
-
 @ 472f440f:5669301e
2025-05-12 23:29:50
@ 472f440f:5669301e
2025-05-12 23:29:50Marty's Bent
Last week we covered the bombshell developments in the Samourai Wallet case. For those who didn't read that, last Monday the world was made aware of the fact that the SDNY was explicitly told by FinCEN that the federal regulator did not believe that Samourai Wallet was a money services business six months before arresting the co-founders of Samourai Wallet for conspiracy to launder money and illegally operating a money services business. This was an obvious overstep by the SDNY that many believed would be quickly alleviated, especially considering the fact that the Trump administration via the Department of Justice has made it clear that they do not intend to rule via prosecution.
It seems that this is not the case as the SDNY responded to a letter sent from the defense to dismiss the case by stating that they fully plan to move forward. Stating that they only sought the recommendations of FinCEN employees and did not believe that those employees' comments were indicative of FinCEN's overall views on this particular case. It's a pretty egregious abuse of power by the SDNY. I'm not sure if the particular lawyers and judges within the Southern District of New York are very passionate about preventing the use of self-custody bitcoin and products that enable bitcoiners to transact privately, or if they're simply participating in a broader meta war with the Trump administration - who has made it clear to federal judges across the country that last Fall's election will have consequences, mainly that the Executive Branch will try to effectuate the policies that President Trump campaigned on by any legal means necessary - and Samouari Wallet is simply in the middle of that meta war.
However, one thing is pretty clear to me, this is an egregious overstep of power. The interpretation of that law, as has been laid out and confirmed by FinCEN over the last decade, is pretty clear; you cannot be a money services business if you do not control the funds that people are sending to each other, which is definitely the case with Samourai Wallet. People downloaded Samourai Wallet, spun up their own private-public key pairs and initiated transactions themselves. Samourai never custodied funds or initiated transactions on behalf of their users. This is very cut and dry. Straight to the point. It should be something that anyone with more than two brain cells is able to discern pretty quickly.
It is imperative that anybody in the industry who cares about being able to hold bitcoin in self-custody, to mine bitcoin, and to send bitcoin in a peer-to-peer fashion makes some noise around this case. None of the current administration's attempts to foster innovation around bitcoin in the United States will matter if the wrong precedent is set in this case. If the SDNY is successful in prosecuting Samourai Wallet, it will mean that anybody holding Bitcoin in self-custody, running a bitcoin fold node or mining bitcoin will have to KYC all of their users and counterparts lest they be labeled a money services business that is breaking laws stemming from the Bank Secrecy Act. This will effectively make building a self-custody bitcoin wallet, running a node, or mining bitcoin in tillegal in the United States. The ability to comply with the rules that would be unleashed if this Samourai case goes the wrong way, are such that it will effectively destroy the industry overnight.
It is yet to be seen whether or not the Department of Justice will step in to publicly flog the SDNY and force them to stop pursuing this case. This is the only likely way that the case will go away at this point, so it is very important that bitcoiners who care about being able to self-custody bitcoin, mine bitcoin, or send bitcoin in a peer-to-peer fashion in the United States make it clear to the current administration and any local politicians that this is an issue that you care deeply about. If we are too complacent, there is a chance that the SDNY could completely annihilate the bitcoin industry in America despite of all of the positive momentum we're seeing from all angles at the moment.
Make some noise!
Bitcoin Adoption by Power Companies: The Next Frontier
In my recent conversation with Andrew Myers from Satoshi Energy, he shared their ambitious mission to "enable every electric power company to use bitcoin by block 1,050,000" – roughly three years from now. This strategic imperative isn't just about creating new Bitcoin users; it's about sovereignty. Andrew emphasized that getting Bitcoin into the hands of energy companies who value self-sovereignty creates a more balanced future economic landscape. The excitement was palpable as he described how several energy companies are already moving beyond simply selling power to Bitcoin miners and are beginning to invest in mining operations themselves.
"You have global commodity companies being like, 'Oh, this is another commodity – we want to invest in this, we want to own this,'" - Andrew Myers
Perhaps most fascinating was Andrew's revelation about major energy companies in Texas developing Bitcoin collateral products for power contracts – a practical application that could revolutionize how energy transactions are settled. As energy companies continue embracing Bitcoin for both operations and collateral, we're witnessing the early stages of a profound shift in how critical infrastructure interfaces with sound money. The implications for both sectors could be transformative.
Check out the full podcast here for more on remote viewing, Nikola Tesla's predictions, and the convergence of Bitcoin and AI technology. We cover everything from humanoid robots to the energy demands of next-generation computing.
Headlines of the Day
Steak n Shake to Accept Bitcoin at All Locations May 16 - via X
Facebook Plans Crypto Wallets for 3B Users, Bitcoin Impact Looms - via X
Trump Urges Americans to Buy Stocks for Economic Boom - via X
UK Drops Tariffs, U.S. Farmers Set to Reap Major Benefits - via X
Looking for the perfect video to push the smartest person you know from zero to one on bitcoin? Bitcoin, Not Crypto is a three-part master class from Parker Lewis and Dhruv Bansal that cuts through the noise—covering why 21 million was the key technical simplification that made bitcoin possible, why blockchains don’t create decentralization, and why everything else will be built on bitcoin.
Ten31, the largest bitcoin-focused investor, has deployed 145,630 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
Happy belated Mother's Day to all the moms out there.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ 3b3a42d3:d192e325
2025-04-10 08:57:51
@ 3b3a42d3:d192e325
2025-04-10 08:57:51Atomic Signature Swaps (ASS) over Nostr is a protocol for atomically exchanging Schnorr signatures using Nostr events for orchestration. This new primitive enables multiple interesting applications like:
- Getting paid to publish specific Nostr events
- Issuing automatic payment receipts
- Contract signing in exchange for payment
- P2P asset exchanges
- Trading and enforcement of asset option contracts
- Payment in exchange for Nostr-based credentials or access tokens
- Exchanging GMs 🌞
It only requires that (i) the involved signatures be Schnorr signatures using the secp256k1 curve and that (ii) at least one of those signatures be accessible to both parties. These requirements are naturally met by Nostr events (published to relays), Taproot transactions (published to the mempool and later to the blockchain), and Cashu payments (using mints that support NUT-07, allowing any pair of these signatures to be swapped atomically.
How the Cryptographic Magic Works 🪄
This is a Schnorr signature
(Zₓ, s):s = z + H(Zₓ || P || m)⋅kIf you haven't seen it before, don't worry, neither did I until three weeks ago.
The signature scalar s is the the value a signer with private key
k(and public keyP = k⋅G) must calculate to prove his commitment over the messagemgiven a randomly generated noncez(Zₓis just the x-coordinate of the public pointZ = z⋅G).His a hash function (sha256 with the tag "BIP0340/challenge" when dealing with BIP340),||just means to concatenate andGis the generator point of the elliptic curve, used to derive public values from private ones.Now that you understand what this equation means, let's just rename
z = r + t. We can do that,zis just a randomly generated number that can be represented as the sum of two other numbers. It also follows thatz⋅G = r⋅G + t⋅G ⇔ Z = R + T. Putting it all back into the definition of a Schnorr signature we get:s = (r + t) + H((R + T)ₓ || P || m)⋅kWhich is the same as:
s = sₐ + twheresₐ = r + H((R + T)ₓ || P || m)⋅ksₐis what we call the adaptor signature scalar) and t is the secret.((R + T)ₓ, sₐ)is an incomplete signature that just becomes valid by add the secret t to thesₐ:s = sₐ + tWhat is also important for our purposes is that by getting access to the valid signature s, one can also extract t from it by just subtracting
sₐ:t = s - sₐThe specific value of
tdepends on our choice of the public pointT, sinceRis just a public point derived from a randomly generated noncer.So how do we choose
Tso that it requires the secret t to be the signature over a specific messagem'by an specific public keyP'? (without knowing the value oft)Let's start with the definition of t as a valid Schnorr signature by P' over m':
t = r' + H(R'ₓ || P' || m')⋅k' ⇔ t⋅G = r'⋅G + H(R'ₓ || P' || m')⋅k'⋅GThat is the same as:
T = R' + H(R'ₓ || P' || m')⋅P'Notice that in order to calculate the appropriate
Tthat requirestto be an specific signature scalar, we only need to know the public nonceR'used to generate that signature.In summary: in order to atomically swap Schnorr signatures, one party
P'must provide a public nonceR', while the other partyPmust provide an adaptor signature using that nonce:sₐ = r + H((R + T)ₓ || P || m)⋅kwhereT = R' + H(R'ₓ || P' || m')⋅P'P'(the nonce provider) can then add his own signature t to the adaptor signaturesₐin order to get a valid signature byP, i.e.s = sₐ + t. When he publishes this signature (as a Nostr event, Cashu transaction or Taproot transaction), it becomes accessible toPthat can now extract the signaturetbyP'and also make use of it.Important considerations
A signature may not be useful at the end of the swap if it unlocks funds that have already been spent, or that are vulnerable to fee bidding wars.
When a swap involves a Taproot UTXO, it must always use a 2-of-2 multisig timelock to avoid those issues.
Cashu tokens do not require this measure when its signature is revealed first, because the mint won't reveal the other signature if they can't be successfully claimed, but they also require a 2-of-2 multisig timelock when its signature is only revealed last (what is unavoidable in cashu for cashu swaps).
For Nostr events, whoever receives the signature first needs to publish it to at least one relay that is accessible by the other party. This is a reasonable expectation in most cases, but may be an issue if the event kind involved is meant to be used privately.
How to Orchestrate the Swap over Nostr?
Before going into the specific event kinds, it is important to recognize what are the requirements they must meet and what are the concerns they must address. There are mainly three requirements:
- Both parties must agree on the messages they are going to sign
- One party must provide a public nonce
- The other party must provide an adaptor signature using that nonce
There is also a fundamental asymmetry in the roles of both parties, resulting in the following significant downsides for the party that generates the adaptor signature:
- NIP-07 and remote signers do not currently support the generation of adaptor signatures, so he must either insert his nsec in the client or use a fork of another signer
- There is an overhead of retrieving the completed signature containing the secret, either from the blockchain, mint endpoint or finding the appropriate relay
- There is risk he may not get his side of the deal if the other party only uses his signature privately, as I have already mentioned
- There is risk of losing funds by not extracting or using the signature before its timelock expires. The other party has no risk since his own signature won't be exposed by just not using the signature he received.
The protocol must meet all those requirements, allowing for some kind of role negotiation and while trying to reduce the necessary hops needed to complete the swap.
Swap Proposal Event (kind:455)
This event enables a proposer and his counterparty to agree on the specific messages whose signatures they intend to exchange. The
contentfield is the following stringified JSON:{ "give": <signature spec (required)>, "take": <signature spec (required)>, "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>", "description": "<Info about the proposal (optional)>", "nonce": "<Signature public nonce (optional)>", "enc_s": "<Encrypted signature scalar (optional)>" }The field
roleindicates what the proposer will provide during the swap, either the nonce or the adaptor. When this optional field is not provided, the counterparty may decide whether he will send a nonce back in a Swap Nonce event or a Swap Adaptor event using thenonce(optionally) provided by in the Swap Proposal in order to avoid one hop of interaction.The
enc_sfield may be used to store the encrypted scalar of the signature associated with thenonce, since this information is necessary later when completing the adaptor signature received from the other party.A
signature specspecifies thetypeand all necessary information for producing and verifying a given signature. In the case of signatures for Nostr events, it contain a template with all the fields, exceptpubkey,idandsig:{ "type": "nostr", "template": { "kind": "<kind>" "content": "<content>" "tags": [ … ], "created_at": "<created_at>" } }In the case of Cashu payments, a simplified
signature specjust needs to specify the payment amount and an array of mints trusted by the proposer:{ "type": "cashu", "amount": "<amount>", "mint": ["<acceptable mint_url>", …] }This works when the payer provides the adaptor signature, but it still needs to be extended to also work when the payer is the one receiving the adaptor signature. In the later case, the
signature specmust also include atimelockand the derived public keysYof each Cashu Proof, but for now let's just ignore this situation. It should be mentioned that the mint must be trusted by both parties and also support Token state check (NUT-07) for revealing the completed adaptor signature and P2PK spending conditions (NUT-11) for the cryptographic scheme to work.The
tagsare:"p", the proposal counterparty's public key (required)"a", akind:30455Swap Listing event or an application specific version of it (optional)
Forget about this Swap Listing event for now, I will get to it later...
Swap Nonce Event (kind:456) - Optional
This is an optional event for the Swap Proposal receiver to provide the public nonce of his signature when the proposal does not include a nonce or when he does not want to provide the adaptor signature due to the downsides previously mentioned. The
contentfield is the following stringified JSON:{ "nonce": "<Signature public nonce>", "enc_s": "<Encrypted signature scalar (optional)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Swap Adaptor Event (kind:457)
The
contentfield is the following stringified JSON:{ "adaptors": [ { "sa": "<Adaptor signature scalar>", "R": "<Signer's public nonce (including parity byte)>", "T": "<Adaptor point (including parity byte)>", "Y": "<Cashu proof derived public key (if applicable)>", }, …], "cashu": "<Cashu V4 token (if applicable)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Discoverability
The Swap Listing event previously mentioned as an optional tag in the Swap Proposal may be used to find an appropriate counterparty for a swap. It allows a user to announce what he wants to accomplish, what his requirements are and what is still open for negotiation.
Swap Listing Event (kind:30455)
The
contentfield is the following stringified JSON:{ "description": "<Information about the listing (required)>", "give": <partial signature spec (optional)>, "take": <partial signature spec (optional)>, "examples: [<take signature spec>], // optional "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>" }The
descriptionfield describes the restrictions on counterparties and signatures the user is willing to accept.A
partial signature specis an incompletesignature specused in Swap Proposal eventskind:455where omitting fields signals that they are still open for negotiation.The
examplesfield is an array ofsignature specsthe user would be willing totake.The
tagsare:"d", a unique listing id (required)"s", the status of the listingdraft | open | closed(required)"t", topics related to this listing (optional)"p", public keys to notify about the proposal (optional)
Application Specific Swap Listings
Since Swap Listings are still fairly generic, it is expected that specific use cases define new event kinds based on the generic listing. Those application specific swap listing would be easier to filter by clients and may impose restrictions and add new fields and/or tags. The following are some examples under development:
Sponsored Events
This listing is designed for users looking to promote content on the Nostr network, as well as for those who want to monetize their accounts by sharing curated sponsored content with their existing audiences.
It follows the same format as the generic Swap Listing event, but uses the
kind:30456instead.The following new tags are included:
"k", event kind being sponsored (required)"title", campaign title (optional)
It is required that at least one
signature spec(giveand/ortake) must have"type": "nostr"and also contain the following tag["sponsor", "<pubkey>", "<attestation>"]with the sponsor's public key and his signature over the signature spec without the sponsor tag as his attestation. This last requirement enables clients to disclose and/or filter sponsored events.Asset Swaps
This listing is designed for users looking for counterparties to swap different assets that can be transferred using Schnorr signatures, like any unit of Cashu tokens, Bitcoin or other asset IOUs issued using Taproot.
It follows the same format as the generic Swap Listing event, but uses the
kind:30457instead.It requires the following additional tags:
"t", asset pair to be swapped (e.g."btcusd")"t", asset being offered (e.g."btc")"t", accepted payment method (e.g."cashu","taproot")
Swap Negotiation
From finding an appropriate Swap Listing to publishing a Swap Proposal, there may be some kind of negotiation between the involved parties, e.g. agreeing on the amount to be paid by one of the parties or the exact content of a Nostr event signed by the other party. There are many ways to accomplish that and clients may implement it as they see fit for their specific goals. Some suggestions are:
- Adding
kind:1111Comments to the Swap Listing or an existing Swap Proposal - Exchanging tentative Swap Proposals back and forth until an agreement is reached
- Simple exchanges of DMs
- Out of band communication (e.g. Signal)
Work to be done
I've been refining this specification as I develop some proof-of-concept clients to experience its flaws and trade-offs in practice. I left the signature spec for Taproot signatures out of the current document as I still have to experiment with it. I will probably find some important orchestration issues related to dealing with
2-of-2 multisig timelocks, which also affects Cashu transactions when spent last, that may require further adjustments to what was presented here.The main goal of this article is to find other people interested in this concept and willing to provide valuable feedback before a PR is opened in the NIPs repository for broader discussions.
References
- GM Swap- Nostr client for atomically exchanging GM notes. Live demo available here.
- Sig4Sats Script - A Typescript script demonstrating the swap of a Cashu payment for a signed Nostr event.
- Loudr- Nostr client under development for sponsoring the publication of Nostr events. Live demo available at loudr.me.
- Poelstra, A. (2017). Scriptless Scripts. Blockstream Research. https://github.com/BlockstreamResearch/scriptless-scripts
-
 @ eab58da0:eebdafbf
2025-05-13 05:16:32
@ eab58da0:eebdafbf
2025-05-13 05:16:32Hey there, it’s me. Someone who used to run through life like it was a marathon with no finish line. For years, I chased everything: the perfect job, the dream apartment, the Instagram-worthy moments.
I’d wake up exhausted, convinced I was one step behind where I should be. That was my normal—until the day I just… stopped.
The breaking point. It was a rainy Tuesday, and I’d just bombed a big presentation at work. My inbox was overflowing, my coffee was cold, and I felt like a failure. I remember sitting on my couch, staring at the wall, thinking, “What’s the point?” I’d been chasing this idea of success, but it kept moving further away. That’s when it hit me—I wasn’t living. I was just running.
So, I did something radical: nothing. I turned off my phone, made a cup of tea, and sat in silence. No goals, no to-do lists, just me and the rain tapping on the window. It felt weird at first—like I was breaking some unwritten rule—but then it felt… freeing. I started small after that. Walks without a podcast. Cooking without rushing. Saying no to things that didn’t light me up. I stopped chasing and started showing up for the life I already had.
Looking Back. Now, months later, I see that day as a turning point. I still have dreams, but they don’t own me anymore. I’ve learned to savor the messy, quiet moments—the ones I used to overlook. Life’s not perfect, but it’s mine. And honestly? That’s enough.
-
 @ eaccf0cb:23be2b8f
2025-05-13 05:02:24
@ eaccf0cb:23be2b8f
2025-05-13 05:02:24Trong thời đại công nghệ phát triển nhanh chóng, việc tìm kiếm một nền tảng số toàn diện, thân thiện và ổn định đã trở thành nhu cầu thiết yếu đối với người dùng. LU8 chính là câu trả lời cho nhu cầu đó, khi mang đến một hệ sinh thái tích hợp với giao diện thông minh, cấu trúc hợp lý và tốc độ xử lý vượt trội. Mọi thao tác trên LU8 đều được thiết kế để tối giản hóa quá trình sử dụng, từ việc đăng ký, truy cập đến thao tác các tiện ích bên trong. Tính năng tương thích đa nền tảng là một trong những điểm mạnh nổi bật, cho phép người dùng sử dụng LU8 linh hoạt trên điện thoại, máy tính bảng hoặc máy tính cá nhân mà không gặp bất kỳ rào cản nào về kỹ thuật hay hiệu suất. Ngoài ra, LU8 thường xuyên cập nhật các xu hướng công nghệ mới, giúp hệ thống luôn vận hành trơn tru và đáp ứng kịp thời những thay đổi trong hành vi người dùng. Việc áp dụng các thuật toán tối ưu hóa hiệu suất cũng giúp thời gian phản hồi của hệ thống nhanh hơn, mang lại trải nghiệm liền mạch cho người dùng ở mọi hoàn cảnh.
Không chỉ dừng lại ở khả năng vận hành mượt mà, LU8 còn đặc biệt chú trọng đến yếu tố bảo mật và sự an toàn thông tin cá nhân cho người sử dụng. Hệ thống được xây dựng trên nền tảng mã hóa hiện đại, sử dụng nhiều lớp xác thực và kiểm tra chéo để ngăn chặn các rủi ro đến từ bên ngoài. Việc này không chỉ giúp bảo vệ dữ liệu một cách toàn diện mà còn tăng cường mức độ tin cậy từ phía người dùng, đặc biệt là trong những hoạt động yêu cầu tính riêng tư cao. LU8 còn cung cấp các tùy chọn bảo mật nâng cao như xác minh qua email, mã OTP và các công cụ nhận diện thiết bị truy cập để hỗ trợ người dùng quản lý tài khoản một cách hiệu quả nhất. Ngoài ra, quá trình sao lưu dữ liệu được thực hiện định kỳ, đảm bảo không có sự cố mất mát nào ảnh hưởng đến trải nghiệm tổng thể. Đội ngũ kỹ thuật đứng sau LU8 luôn theo dõi hệ thống liên tục, nhằm phát hiện và khắc phục mọi sự cố có thể xảy ra trong thời gian ngắn nhất. Những yếu tố này cho thấy LU8 không chỉ là một nền tảng công nghệ hiện đại, mà còn là một hệ thống được đầu tư bài bản với mục tiêu dài hạn.
Bên cạnh sự mạnh mẽ về công nghệ và bảo mật, LU8 còn tạo nên khác biệt thông qua chất lượng chăm sóc khách hàng vượt trội. Với hệ thống hỗ trợ trực tuyến hoạt động liên tục 24/7, người dùng luôn nhận được sự hỗ trợ tận tình, nhanh chóng và chính xác từ đội ngũ chuyên viên. Mọi thắc mắc, từ đơn giản đến phức tạp, đều được giải đáp cặn kẽ, giúp người dùng an tâm hơn khi tương tác với nền tảng. LU8 cũng duy trì một kênh phản hồi mở, nơi người dùng có thể gửi góp ý để cải thiện chất lượng dịch vụ. Các ý kiến này không bị bỏ qua mà luôn được phân tích và áp dụng vào quá trình nâng cấp hệ thống nhằm phục vụ người dùng tốt hơn mỗi ngày. Ngoài ra, LU8 thường xuyên triển khai các chương trình tri ân khách hàng, khuyến khích sự gắn bó lâu dài và xây dựng cộng đồng người dùng tích cực. Trong tương lai, LU8 đặt mục tiêu mở rộng hơn nữa phạm vi ứng dụng và tích hợp thêm nhiều tiện ích mới, tạo nên một nền tảng số toàn diện, đáp ứng đa dạng nhu cầu của người dùng hiện đại và không ngừng thích ứng với xu hướng công nghệ toàn cầu.
-
 @ 472f440f:5669301e
2025-05-12 23:29:19
@ 472f440f:5669301e
2025-05-12 23:29:19Marty's Bent
Last week we covered the bombshell developments in the Samourai Wallet case. For those who didn't read that, last Monday the world was made aware of the fact that the SDNY was explicitly told by FinCEN that the federal regulator did not believe that Samourai Wallet was a money services business six months before arresting the co-founders of Samourai Wallet for conspiracy to launder money and illegally operating a money services business. This was an obvious overstep by the SDNY that many believed would be quickly alleviated, especially considering the fact that the Trump administration via the Department of Justice has made it clear that they do not intend to rule via prosecution.
It seems that this is not the case as the SDNY responded to a letter sent from the defense to dismiss the case by stating that they fully plan to move forward. Stating that they only sought the recommendations of FinCEN employees and did not believe that those employees' comments were indicative of FinCEN's overall views on this particular case. It's a pretty egregious abuse of power by the SDNY. I'm not sure if the particular lawyers and judges within the Southern District of New York are very passionate about preventing the use of self-custody bitcoin and products that enable bitcoiners to transact privately, or if they're simply participating in a broader meta war with the Trump administration - who has made it clear to federal judges across the country that last Fall's election will have consequences, mainly that the Executive Branch will try to effectuate the policies that President Trump campaigned on by any legal means necessary - and Samouari Wallet is simply in the middle of that meta war.
However, one thing is pretty clear to me, this is an egregious overstep of power. The interpretation of that law, as has been laid out and confirmed by FinCEN over the last decade, is pretty clear; you cannot be a money services business if you do not control the funds that people are sending to each other, which is definitely the case with Samourai Wallet. People downloaded Samourai Wallet, spun up their own private-public key pairs and initiated transactions themselves. Samourai never custodied funds or initiated transactions on behalf of their users. This is very cut and dry. Straight to the point. It should be something that anyone with more than two brain cells is able to discern pretty quickly.
It is imperative that anybody in the industry who cares about being able to hold bitcoin in self-custody, to mine bitcoin, and to send bitcoin in a peer-to-peer fashion makes some noise around this case. None of the current administration's attempts to foster innovation around bitcoin in the United States will matter if the wrong precedent is set in this case. If the SDNY is successful in prosecuting Samourai Wallet, it will mean that anybody holding Bitcoin in self-custody, running a bitcoin fold node or mining bitcoin will have to KYC all of their users and counterparts lest they be labeled a money services business that is breaking laws stemming from the Bank Secrecy Act. This will effectively make building a self-custody bitcoin wallet, running a node, or mining bitcoin in tillegal in the United States. The ability to comply with the rules that would be unleashed if this Samourai case goes the wrong way, are such that it will effectively destroy the industry overnight.
It is yet to be seen whether or not the Department of Justice will step in to publicly flog the SDNY and force them to stop pursuing this case. This is the only likely way that the case will go away at this point, so it is very important that bitcoiners who care about being able to self-custody bitcoin, mine bitcoin, or send bitcoin in a peer-to-peer fashion in the United States make it clear to the current administration and any local politicians that this is an issue that you care deeply about. If we are too complacent, there is a chance that the SDNY could completely annihilate the bitcoin industry in America despite of all of the positive momentum we're seeing from all angles at the moment.
Make some noise!
Bitcoin Adoption by Power Companies: The Next Frontier
In my recent conversation with Andrew Myers from Satoshi Energy, he shared their ambitious mission to "enable every electric power company to use bitcoin by block 1,050,000" – roughly three years from now. This strategic imperative isn't just about creating new Bitcoin users; it's about sovereignty. Andrew emphasized that getting Bitcoin into the hands of energy companies who value self-sovereignty creates a more balanced future economic landscape. The excitement was palpable as he described how several energy companies are already moving beyond simply selling power to Bitcoin miners and are beginning to invest in mining operations themselves.
"You have global commodity companies being like, 'Oh, this is another commodity – we want to invest in this, we want to own this,'" - Andrew Myers
Perhaps most fascinating was Andrew's revelation about major energy companies in Texas developing Bitcoin collateral products for power contracts – a practical application that could revolutionize how energy transactions are settled. As energy companies continue embracing Bitcoin for both operations and collateral, we're witnessing the early stages of a profound shift in how critical infrastructure interfaces with sound money. The implications for both sectors could be transformative.
Check out the full podcast here for more on remote viewing, Nikola Tesla's predictions, and the convergence of Bitcoin and AI technology. We cover everything from humanoid robots to the energy demands of next-generation computing.
Headlines of the Day
Steak n Shake to Accept Bitcoin at All Locations May 16 - via X
Facebook Plans Crypto Wallets for 3B Users, Bitcoin Impact Looms - via X
Trump Urges Americans to Buy Stocks for Economic Boom - via X
UK Drops Tariffs, U.S. Farmers Set to Reap Major Benefits - via X
Looking for the perfect video to push the smartest person you know from zero to one on bitcoin? Bitcoin, Not Crypto is a three-part master class from Parker Lewis and Dhruv Bansal that cuts through the noise—covering why 21 million was the key technical simplification that made bitcoin possible, why blockchains don’t create decentralization, and why everything else will be built on bitcoin.
Ten31, the largest bitcoin-focused investor, has deployed 145,630 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
Happy belated Mother's Day to all the moms out there.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ 66675158:1b644430
2025-03-23 11:39:41
@ 66675158:1b644430
2025-03-23 11:39:41I don't believe in "vibe coding" – it's just the newest Silicon Valley fad trying to give meaning to their latest favorite technology, LLMs. We've seen this pattern before with blockchain, when suddenly Non Fungible Tokens appeared, followed by Web3 startups promising to revolutionize everything from social media to supply chains. VCs couldn't throw money fast enough at anything with "decentralized" (in name only) in the pitch deck. Andreessen Horowitz launched billion-dollar crypto funds, while Y Combinator batches filled with blockchain startups promising to be "Uber for X, but on the blockchain."
The metaverse mania followed, with Meta betting its future on digital worlds where we'd supposedly hang out as legless avatars. Decentralized (in name only) autonomous organizations emerged as the next big thing – supposedly democratic internet communities that ended up being the next scam for quick money.
Then came the inevitable collapse. The FTX implosion in late 2022 revealed fraud, Luna/Terra's death spiral wiped out billions (including my ten thousand dollars), while Celsius and BlockFi froze customer assets before bankruptcy.
By 2023, crypto winter had fully set in. The SEC started aggressive enforcement actions, while users realized that blockchain technology had delivered almost no practical value despite a decade of promises.
Blockchain's promises tapped into fundamental human desires – decentralization resonated with a generation disillusioned by traditional institutions. Evangelists presented a utopian vision of freedom from centralized control. Perhaps most significantly, crypto offered a sense of meaning in an increasingly abstract world, making the clear signs of scams harder to notice.
The technology itself had failed to solve any real-world problems at scale. By 2024, the once-mighty crypto ecosystem had become a cautionary tale. Venture firms quietly scrubbed blockchain references from their websites while founders pivoted to AI and large language models.
Most reading this are likely fellow bitcoiners and nostr users who understand that Bitcoin is blockchain's only valid use case. But I shared that painful history because I believe the AI-hype cycle will follow the same trajectory.
Just like with blockchain, we're now seeing VCs who once couldn't stop talking about "Web3" falling over themselves to fund anything with "AI" in the pitch deck. The buzzwords have simply changed from "decentralized" to "intelligent."
"Vibe coding" is the perfect example – a trendy name for what is essentially just fuzzy instructions to LLMs. Developers who've spent years honing programming skills are now supposed to believe that "vibing" with an AI is somehow a legitimate methodology.
This might be controversial to some, but obvious to others:
Formal, context-free grammar will always remain essential for building precise systems, regardless of how advanced natural language technology becomes
The mathematical precision of programming languages provides a foundation that human language's ambiguity can never replace. Programming requires precision – languages, compilers, and processors operate on explicit instructions, not vibes. What "vibe coding" advocates miss is that beneath every AI-generated snippet lies the same deterministic rules that have always governed computation.
LLMs don't understand code in any meaningful sense—they've just ingested enormous datasets of human-written code and can predict patterns. When they "work," it's because they've seen similar patterns before, not because they comprehend the underlying logic.
This creates a dangerous dependency. Junior developers "vibing" with LLMs might get working code without understanding the fundamental principles. When something breaks in production, they'll lack the knowledge to fix it.
Even experienced developers can find themselves in treacherous territory when relying too heavily on LLM-generated code. What starts as a productivity boost can transform into a dependency crutch.
The real danger isn't just technical limitations, but the false confidence it instills. Developers begin to believe they understand systems they've merely instructed an AI to generate – fundamentally different from understanding code you've written yourself.
We're already seeing the warning signs: projects cobbled together with LLM-generated code that work initially but become maintenance nightmares when requirements change or edge cases emerge.
The venture capital money is flowing exactly as it did with blockchain. Anthropic raised billions, OpenAI is valued astronomically despite minimal revenue, and countless others are competing to build ever-larger models with vague promises. Every startup now claims to be "AI-powered" regardless of whether it makes sense.
Don't get me wrong—there's genuine innovation happening in AI research. But "vibe coding" isn't it. It's a marketing term designed to make fuzzy prompting sound revolutionary.
Cursor perfectly embodies this AI hype cycle. It's an AI-enhanced code editor built on VS Code that promises to revolutionize programming by letting you "chat with your codebase." Just like blockchain startups promised to "revolutionize" industries, Cursor promises to transform development by adding LLM capabilities.
Yes, Cursor can be genuinely helpful. It can explain unfamiliar code, suggest completions, and help debug simple issues. After trying it for just an hour, I found the autocomplete to be MAGICAL for simple refactoring and basic functionality.
But the marketing goes far beyond reality. The suggestion that you can simply describe what you want and get production-ready code is dangerously misleading. What you get are approximations with:
- Security vulnerabilities the model doesn't understand
- Edge cases it hasn't considered
- Performance implications it can't reason about
- Dependency conflicts it has no way to foresee
The most concerning aspect is how such tools are marketed to beginners as shortcuts around learning fundamentals. "Why spend years learning to code when you can just tell AI what you want?" This is reminiscent of how crypto was sold as a get-rich-quick scheme requiring no actual understanding.
When you "vibe code" with an AI, you're not eliminating complexity—you're outsourcing understanding to a black box. This creates developers who can prompt but not program, who can generate but not comprehend.
The real utility of LLMs in development is in augmenting existing workflows:
- Explaining unfamiliar codebases
- Generating boilerplate for well-understood patterns
- Suggesting implementations that a developer evaluates critically
- Assisting with documentation and testing
These uses involve the model as a subordinate assistant to a knowledgeable developer, not as a replacement for expertise. This is where the technology adds value—as a sophisticated tool in skilled hands.
Cursor is just a better hammer, not a replacement for understanding what you're building. The actual value emerges when used by developers who understand what happens beneath the abstractions. They can recognize when AI suggestions make sense and when they don't because they have the fundamental knowledge to evaluate output critically.
This is precisely where the "vibe coding" narrative falls apart.
-
 @ eac63075:b4988b48
2025-01-04 19:41:34
@ eac63075:b4988b48
2025-01-04 19:41:34Since its creation in 2009, Bitcoin has symbolized innovation and resilience. However, from time to time, alarmist narratives arise about emerging technologies that could "break" its security. Among these, quantum computing stands out as one of the most recurrent. But does quantum computing truly threaten Bitcoin? And more importantly, what is the community doing to ensure the protocol remains invulnerable?
The answer, contrary to sensationalist headlines, is reassuring: Bitcoin is secure, and the community is already preparing for a future where quantum computing becomes a practical reality. Let’s dive into this topic to understand why the concerns are exaggerated and how the development of BIP-360 demonstrates that Bitcoin is one step ahead.
What Is Quantum Computing, and Why Is Bitcoin Not Threatened?
Quantum computing leverages principles of quantum mechanics to perform calculations that, in theory, could exponentially surpass classical computers—and it has nothing to do with what so-called “quantum coaches” teach to scam the uninformed. One of the concerns is that this technology could compromise two key aspects of Bitcoin’s security:
- Wallets: These use elliptic curve algorithms (ECDSA) to protect private keys. A sufficiently powerful quantum computer could deduce a private key from its public key.
- Mining: This is based on the SHA-256 algorithm, which secures the consensus process. A quantum attack could, in theory, compromise the proof-of-work mechanism.
Understanding Quantum Computing’s Attack Priorities
While quantum computing is often presented as a threat to Bitcoin, not all parts of the network are equally vulnerable. Theoretical attacks would be prioritized based on two main factors: ease of execution and potential reward. This creates two categories of attacks:
1. Attacks on Wallets
Bitcoin wallets, secured by elliptic curve algorithms, would be the initial targets due to the relative vulnerability of their public keys, especially those already exposed on the blockchain. Two attack scenarios stand out:
-
Short-term attacks: These occur during the interval between sending a transaction and its inclusion in a block (approximately 10 minutes). A quantum computer could intercept the exposed public key and derive the corresponding private key to redirect funds by creating a transaction with higher fees.
-
Long-term attacks: These focus on old wallets whose public keys are permanently exposed. Wallets associated with Satoshi Nakamoto, for example, are especially vulnerable because they were created before the practice of using hashes to mask public keys.
We can infer a priority order for how such attacks might occur based on urgency and importance.
 Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)
Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)2. Attacks on Mining
Targeting the SHA-256 algorithm, which secures the mining process, would be the next objective. However, this is far more complex and requires a level of quantum computational power that is currently non-existent and far from realization. A successful attack would allow for the recalculation of all possible hashes to dominate the consensus process and potentially "mine" it instantly.
 Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin Attacks
Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin AttacksRecently, Narcelio asked me about a statement I made on Tubacast:
https://x.com/eddieoz/status/1868371296683511969
If an attack became a reality before Bitcoin was prepared, it would be necessary to define the last block prior to the attack and proceed from there using a new hashing algorithm. The solution would resemble the response to the infamous 2013 bug. It’s a fact that this would cause market panic, and Bitcoin's price would drop significantly, creating a potential opportunity for the well-informed.
Preferably, if developers could anticipate the threat and had time to work on a solution and build consensus before an attack, they would simply decide on a future block for the fork, which would then adopt the new algorithm. It might even rehash previous blocks (reaching consensus on them) to avoid potential reorganization through the re-mining of blocks using the old hash. (I often use the term "shielding" old transactions).
How Can Users Protect Themselves?
While quantum computing is still far from being a practical threat, some simple measures can already protect users against hypothetical scenarios:
- Avoid using exposed public keys: Ensure funds sent to old wallets are transferred to new ones that use public key hashes. This reduces the risk of long-term attacks.
- Use modern wallets: Opt for wallets compatible with SegWit or Taproot, which implement better security practices.
- Monitor security updates: Stay informed about updates from the Bitcoin community, such as the implementation of BIP-360, which will introduce quantum-resistant addresses.
- Do not reuse addresses: Every transaction should be associated with a new address to minimize the risk of repeated exposure of the same public key.
- Adopt secure backup practices: Create offline backups of private keys and seeds in secure locations, protected from unauthorized access.
BIP-360 and Bitcoin’s Preparation for the Future
Even though quantum computing is still beyond practical reach, the Bitcoin community is not standing still. A concrete example is BIP-360, a proposal that establishes the technical framework to make wallets resistant to quantum attacks.
BIP-360 addresses three main pillars:
- Introduction of quantum-resistant addresses: A new address format starting with "BC1R" will be used. These addresses will be compatible with post-quantum algorithms, ensuring that stored funds are protected from future attacks.
- Compatibility with the current ecosystem: The proposal allows users to transfer funds from old addresses to new ones without requiring drastic changes to the network infrastructure.
- Flexibility for future updates: BIP-360 does not limit the choice of specific algorithms. Instead, it serves as a foundation for implementing new post-quantum algorithms as technology evolves.
This proposal demonstrates how Bitcoin can adapt to emerging threats without compromising its decentralized structure.
Post-Quantum Algorithms: The Future of Bitcoin Cryptography
The community is exploring various algorithms to protect Bitcoin from quantum attacks. Among the most discussed are:
- Falcon: A solution combining smaller public keys with compact digital signatures. Although it has been tested in limited scenarios, it still faces scalability and performance challenges.
- Sphincs: Hash-based, this algorithm is renowned for its resilience, but its signatures can be extremely large, making it less efficient for networks like Bitcoin’s blockchain.
- Lamport: Created in 1977, it’s considered one of the earliest post-quantum security solutions. Despite its reliability, its gigantic public keys (16,000 bytes) make it impractical and costly for Bitcoin.
Two technologies show great promise and are well-regarded by the community:
- Lattice-Based Cryptography: Considered one of the most promising, it uses complex mathematical structures to create systems nearly immune to quantum computing. Its implementation is still in its early stages, but the community is optimistic.
- Supersingular Elliptic Curve Isogeny: These are very recent digital signature algorithms and require extensive study and testing before being ready for practical market use.
The final choice of algorithm will depend on factors such as efficiency, cost, and integration capability with the current system. Additionally, it is preferable that these algorithms are standardized before implementation, a process that may take up to 10 years.
Why Quantum Computing Is Far from Being a Threat
The alarmist narrative about quantum computing overlooks the technical and practical challenges that still need to be overcome. Among them:
- Insufficient number of qubits: Current quantum computers have only a few hundred qubits, whereas successful attacks would require millions.
- High error rate: Quantum stability remains a barrier to reliable large-scale operations.
- High costs: Building and operating large-scale quantum computers requires massive investments, limiting their use to scientific or specific applications.
Moreover, even if quantum computers make significant advancements, Bitcoin is already adapting to ensure its infrastructure is prepared to respond.
Conclusion: Bitcoin’s Secure Future
Despite advancements in quantum computing, the reality is that Bitcoin is far from being threatened. Its security is ensured not only by its robust architecture but also by the community’s constant efforts to anticipate and mitigate challenges.
The implementation of BIP-360 and the pursuit of post-quantum algorithms demonstrate that Bitcoin is not only resilient but also proactive. By adopting practical measures, such as using modern wallets and migrating to quantum-resistant addresses, users can further protect themselves against potential threats.
Bitcoin’s future is not at risk—it is being carefully shaped to withstand any emerging technology, including quantum computing.
-
 @ eac63075:b4988b48
2024-11-09 17:57:27
@ eac63075:b4988b48
2024-11-09 17:57:27Based on a recent paper that included collaboration from renowned experts such as Lynn Alden, Steve Lee, and Ren Crypto Fish, we discuss in depth how Bitcoin's consensus is built, the main risks, and the complex dynamics of protocol upgrades.
Podcast https://www.fountain.fm/episode/wbjD6ntQuvX5u2G5BccC
Presentation https://gamma.app/docs/Analyzing-Bitcoin-Consensus-Risks-in-Protocol-Upgrades-p66axxjwaa37ksn
1. Introduction to Consensus in Bitcoin
Consensus in Bitcoin is the foundation that keeps the network secure and functional, allowing users worldwide to perform transactions in a decentralized manner without the need for intermediaries. Since its launch in 2009, Bitcoin is often described as an "immutable" system designed to resist changes, and it is precisely this resistance that ensures its security and stability.
The central idea behind consensus in Bitcoin is to create a set of acceptance rules for blocks and transactions, ensuring that all network participants agree on the transaction history. This prevents "double-spending," where the same bitcoin could be used in two simultaneous transactions, something that would compromise trust in the network.
Evolution of Consensus in Bitcoin
Over the years, consensus in Bitcoin has undergone several adaptations, and the way participants agree on changes remains a delicate process. Unlike traditional systems, where changes can be imposed from the top down, Bitcoin operates in a decentralized model where any significant change needs the support of various groups of stakeholders, including miners, developers, users, and large node operators.
Moreover, the update process is extremely cautious, as hasty changes can compromise the network's security. As a result, the philosophy of "don't fix what isn't broken" prevails, with improvements happening incrementally and only after broad consensus among those involved. This model can make progress seem slow but ensures that Bitcoin remains faithful to the principles of security and decentralization.
2. Technical Components of Consensus
Bitcoin's consensus is supported by a set of technical rules that determine what is considered a valid transaction and a valid block on the network. These technical aspects ensure that all nodes—the computers that participate in the Bitcoin network—agree on the current state of the blockchain. Below are the main technical components that form the basis of the consensus.
Validation of Blocks and Transactions
The validation of blocks and transactions is the central point of consensus in Bitcoin. A block is only considered valid if it meets certain criteria, such as maximum size, transaction structure, and the solving of the "Proof of Work" problem. The proof of work, required for a block to be included in the blockchain, is a computational process that ensures the block contains significant computational effort—protecting the network against manipulation attempts.
Transactions, in turn, need to follow specific input and output rules. Each transaction includes cryptographic signatures that prove the ownership of the bitcoins sent, as well as validation scripts that verify if the transaction conditions are met. This validation system is essential for network nodes to autonomously confirm that each transaction follows the rules.
Chain Selection
Another fundamental technical issue for Bitcoin's consensus is chain selection, which becomes especially important in cases where multiple versions of the blockchain coexist, such as after a network split (fork). To decide which chain is the "true" one and should be followed, the network adopts the criterion of the highest accumulated proof of work. In other words, the chain with the highest number of valid blocks, built with the greatest computational effort, is chosen by the network as the official one.
This criterion avoids permanent splits because it encourages all nodes to follow the same main chain, reinforcing consensus.
Soft Forks vs. Hard Forks
In the consensus process, protocol changes can happen in two ways: through soft forks or hard forks. These variations affect not only the protocol update but also the implications for network users:
-
Soft Forks: These are changes that are backward compatible. Only nodes that adopt the new update will follow the new rules, but old nodes will still recognize the blocks produced with these rules as valid. This compatibility makes soft forks a safer option for updates, as it minimizes the risk of network division.
-
Hard Forks: These are updates that are not backward compatible, requiring all nodes to update to the new version or risk being separated from the main chain. Hard forks can result in the creation of a new coin, as occurred with the split between Bitcoin and Bitcoin Cash in 2017. While hard forks allow for deeper changes, they also bring significant risks of network fragmentation.
These technical components form the base of Bitcoin's security and resilience, allowing the system to remain functional and immutable without losing the necessary flexibility to evolve over time.
3. Stakeholders in Bitcoin's Consensus
Consensus in Bitcoin is not decided centrally. On the contrary, it depends on the interaction between different groups of stakeholders, each with their motivations, interests, and levels of influence. These groups play fundamental roles in how changes are implemented or rejected on the network. Below, we explore the six main stakeholders in Bitcoin's consensus.
1. Economic Nodes
Economic nodes, usually operated by exchanges, custody providers, and large companies that accept Bitcoin, exert significant influence over consensus. Because they handle large volumes of transactions and act as a connection point between the Bitcoin ecosystem and the traditional financial system, these nodes have the power to validate or reject blocks and to define which version of the software to follow in case of a fork.
Their influence is proportional to the volume of transactions they handle, and they can directly affect which chain will be seen as the main one. Their incentive is to maintain the network's stability and security to preserve its functionality and meet regulatory requirements.
2. Investors
Investors, including large institutional funds and individual Bitcoin holders, influence consensus indirectly through their impact on the asset's price. Their buying and selling actions can affect Bitcoin's value, which in turn influences the motivation of miners and other stakeholders to continue investing in the network's security and development.
Some institutional investors have agreements with custodians that may limit their ability to act in network split situations. Thus, the impact of each investor on consensus can vary based on their ownership structure and how quickly they can react to a network change.
3. Media Influencers
Media influencers, including journalists, analysts, and popular personalities on social media, have a powerful role in shaping public opinion about Bitcoin and possible updates. These influencers can help educate the public, promote debates, and bring transparency to the consensus process.
On the other hand, the impact of influencers can be double-edged: while they can clarify complex topics, they can also distort perceptions by amplifying or minimizing change proposals. This makes them a force both of support and resistance to consensus.
4. Miners
Miners are responsible for validating transactions and including blocks in the blockchain. Through computational power (hashrate), they also exert significant influence over consensus decisions. In update processes, miners often signal their support for a proposal, indicating that the new version is safe to use. However, this signaling is not always definitive, and miners can change their position if they deem it necessary.
Their incentive is to maximize returns from block rewards and transaction fees, as well as to maintain the value of investments in their specialized equipment, which are only profitable if the network remains stable.
5. Protocol Developers
Protocol developers, often called "Core Developers," are responsible for writing and maintaining Bitcoin's code. Although they do not have direct power over consensus, they possess an informal veto power since they decide which changes are included in the main client (Bitcoin Core). This group also serves as an important source of technical knowledge, helping guide decisions and inform other stakeholders.
Their incentive lies in the continuous improvement of the network, ensuring security and decentralization. Many developers are funded by grants and sponsorships, but their motivations generally include a strong ideological commitment to Bitcoin's principles.
6. Users and Application Developers
This group includes people who use Bitcoin in their daily transactions and developers who build solutions based on the network, such as wallets, exchanges, and payment platforms. Although their power in consensus is less than that of miners or economic nodes, they play an important role because they are responsible for popularizing Bitcoin's use and expanding the ecosystem.
If application developers decide not to adopt an update, this can affect compatibility and widespread acceptance. Thus, they indirectly influence consensus by deciding which version of the protocol to follow in their applications.
These stakeholders are vital to the consensus process, and each group exerts influence according to their involvement, incentives, and ability to act in situations of change. Understanding the role of each makes it clearer how consensus is formed and why it is so difficult to make significant changes to Bitcoin.
4. Mechanisms for Activating Updates in Bitcoin
For Bitcoin to evolve without compromising security and consensus, different mechanisms for activating updates have been developed over the years. These mechanisms help coordinate changes among network nodes to minimize the risk of fragmentation and ensure that updates are implemented in an orderly manner. Here, we explore some of the main methods used in Bitcoin, their advantages and disadvantages, as well as historical examples of significant updates.
Flag Day
The Flag Day mechanism is one of the simplest forms of activating changes. In it, a specific date or block is determined as the activation moment, and all nodes must be updated by that point. This method does not involve prior signaling; participants simply need to update to the new software version by the established day or block.
-
Advantages: Simplicity and predictability are the main benefits of Flag Day, as everyone knows the exact activation date.
-
Disadvantages: Inflexibility can be a problem because there is no way to adjust the schedule if a significant part of the network has not updated. This can result in network splits if a significant number of nodes are not ready for the update.
An example of Flag Day was the Pay to Script Hash (P2SH) update in 2012, which required all nodes to adopt the change to avoid compatibility issues.
BIP34 and BIP9
BIP34 introduced a more dynamic process, in which miners increase the version number in block headers to signal the update. When a predetermined percentage of the last blocks is mined with this new version, the update is automatically activated. This model later evolved with BIP9, which allowed multiple updates to be signaled simultaneously through "version bits," each corresponding to a specific change.
-
Advantages: Allows the network to activate updates gradually, giving more time for participants to adapt.
-
Disadvantages: These methods rely heavily on miner support, which means that if a sufficient number of miners do not signal the update, it can be delayed or not implemented.
BIP9 was used in the activation of SegWit (BIP141) but faced challenges because some miners did not signal their intent to activate, leading to the development of new mechanisms.
User Activated Soft Forks (UASF) and User Resisted Soft Forks (URSF)
To increase the decision-making power of ordinary users, the concept of User Activated Soft Fork (UASF) was introduced, allowing node operators, not just miners, to determine consensus for a change. In this model, nodes set a date to start rejecting blocks that are not in compliance with the new update, forcing miners to adapt or risk having their blocks rejected by the network.
URSF, in turn, is a model where nodes reject blocks that attempt to adopt a specific update, functioning as resistance against proposed changes.
-
Advantages: UASF returns decision-making power to node operators, ensuring that changes do not depend solely on miners.
-
Disadvantages: Both UASF and URSF can generate network splits, especially in cases of strong opposition among different stakeholders.
An example of UASF was the activation of SegWit in 2017, where users supported activation independently of miner signaling, which ended up forcing its adoption.
BIP8 (LOT=True)
BIP8 is an evolution of BIP9, designed to prevent miners from indefinitely blocking a change desired by the majority of users and developers. BIP8 allows setting a parameter called "lockinontimeout" (LOT) as true, which means that if the update has not been fully signaled by a certain point, it is automatically activated.
-
Advantages: Ensures that changes with broad support among users are not blocked by miners who wish to maintain the status quo.
-
Disadvantages: Can lead to network splits if miners or other important stakeholders do not support the update.
Although BIP8 with LOT=True has not yet been used in Bitcoin, it is a proposal that can be applied in future updates if necessary.
These activation mechanisms have been essential for Bitcoin's development, allowing updates that keep the network secure and functional. Each method brings its own advantages and challenges, but all share the goal of preserving consensus and network cohesion.
5. Risks and Considerations in Consensus Updates
Consensus updates in Bitcoin are complex processes that involve not only technical aspects but also political, economic, and social considerations. Due to the network's decentralized nature, each change brings with it a set of risks that need to be carefully assessed. Below, we explore some of the main challenges and future scenarios, as well as the possible impacts on stakeholders.
Network Fragility with Alternative Implementations
One of the main risks associated with consensus updates is the possibility of network fragmentation when there are alternative software implementations. If an update is implemented by a significant group of nodes but rejected by others, a network split (fork) can occur. This creates two competing chains, each with a different version of the transaction history, leading to unpredictable consequences for users and investors.
Such fragmentation weakens Bitcoin because, by dividing hashing power (computing) and coin value, it reduces network security and investor confidence. A notable example of this risk was the fork that gave rise to Bitcoin Cash in 2017 when disagreements over block size resulted in a new chain and a new asset.
Chain Splits and Impact on Stakeholders
Chain splits are a significant risk in update processes, especially in hard forks. During a hard fork, the network is split into two separate chains, each with its own set of rules. This results in the creation of a new coin and leaves users with duplicated assets on both chains. While this may seem advantageous, in the long run, these splits weaken the network and create uncertainties for investors.
Each group of stakeholders reacts differently to a chain split:
-
Institutional Investors and ETFs: Face regulatory and compliance challenges because many of these assets are managed under strict regulations. The creation of a new coin requires decisions to be made quickly to avoid potential losses, which may be hampered by regulatory constraints.
-
Miners: May be incentivized to shift their computing power to the chain that offers higher profitability, which can weaken one of the networks.
-
Economic Nodes: Such as major exchanges and custody providers, have to quickly choose which chain to support, influencing the perceived value of each network.
Such divisions can generate uncertainties and loss of value, especially for institutional investors and those who use Bitcoin as a store of value.
Regulatory Impacts and Institutional Investors
With the growing presence of institutional investors in Bitcoin, consensus changes face new compliance challenges. Bitcoin ETFs, for example, are required to follow strict rules about which assets they can include and how chain split events should be handled. The creation of a new asset or migration to a new chain can complicate these processes, creating pressure for large financial players to quickly choose a chain, affecting the stability of consensus.
Moreover, decisions regarding forks can influence the Bitcoin futures and derivatives market, affecting perception and adoption by new investors. Therefore, the need to avoid splits and maintain cohesion is crucial to attract and preserve the confidence of these investors.
Security Considerations in Soft Forks and Hard Forks
While soft forks are generally preferred in Bitcoin for their backward compatibility, they are not without risks. Soft forks can create different classes of nodes on the network (updated and non-updated), which increases operational complexity and can ultimately weaken consensus cohesion. In a network scenario with fragmentation of node classes, Bitcoin's security can be affected, as some nodes may lose part of the visibility over updated transactions or rules.
In hard forks, the security risk is even more evident because all nodes need to adopt the new update to avoid network division. Experience shows that abrupt changes can create temporary vulnerabilities, in which malicious agents try to exploit the transition to attack the network.
Bounty Claim Risks and Attack Scenarios
Another risk in consensus updates are so-called "bounty claims"—accumulated rewards that can be obtained if an attacker manages to split or deceive a part of the network. In a conflict scenario, a group of miners or nodes could be incentivized to support a new update or create an alternative version of the software to benefit from these rewards.
These risks require stakeholders to carefully assess each update and the potential vulnerabilities it may introduce. The possibility of "bounty claims" adds a layer of complexity to consensus because each interest group may see a financial opportunity in a change that, in the long term, may harm network stability.
The risks discussed above show the complexity of consensus in Bitcoin and the importance of approaching it gradually and deliberately. Updates need to consider not only technical aspects but also economic and social implications, in order to preserve Bitcoin's integrity and maintain trust among stakeholders.
6. Recommendations for the Consensus Process in Bitcoin
To ensure that protocol changes in Bitcoin are implemented safely and with broad support, it is essential that all stakeholders adopt a careful and coordinated approach. Here are strategic recommendations for evaluating, supporting, or rejecting consensus updates, considering the risks and challenges discussed earlier, along with best practices for successful implementation.
1. Careful Evaluation of Proposal Maturity
Stakeholders should rigorously assess the maturity level of a proposal before supporting its implementation. Updates that are still experimental or lack a robust technical foundation can expose the network to unnecessary risks. Ideally, change proposals should go through an extensive testing phase, have security audits, and receive review and feedback from various developers and experts.
2. Extensive Testing in Secure and Compatible Networks
Before an update is activated on the mainnet, it is essential to test it on networks like testnet and signet, and whenever possible, on other compatible networks that offer a safe and controlled environment to identify potential issues. Testing on networks like Litecoin was fundamental for the safe launch of innovations like SegWit and the Lightning Network, allowing functionalities to be validated on a lower-impact network before being implemented on Bitcoin.
The Liquid Network, developed by Blockstream, also plays an important role as an experimental network for new proposals, such as OP_CAT. By adopting these testing environments, stakeholders can mitigate risks and ensure that the update is reliable and secure before being adopted by the main network.
3. Importance of Stakeholder Engagement
The success of a consensus update strongly depends on the active participation of all stakeholders. This includes economic nodes, miners, protocol developers, investors, and end users. Lack of participation can lead to inadequate decisions or even future network splits, which would compromise Bitcoin's security and stability.
4. Key Questions for Evaluating Consensus Proposals
To assist in decision-making, each group of stakeholders should consider some key questions before supporting a consensus change:
- Does the proposal offer tangible benefits for Bitcoin's security, scalability, or usability?
- Does it maintain backward compatibility or introduce the risk of network split?
- Are the implementation requirements clear and feasible for each group involved?
- Are there clear and aligned incentives for all stakeholder groups to accept the change?
5. Coordination and Timing in Implementations
Timing is crucial. Updates with short activation windows can force a split because not all nodes and miners can update simultaneously. Changes should be planned with ample deadlines to allow all stakeholders to adjust their systems, avoiding surprises that could lead to fragmentation.
Mechanisms like soft forks are generally preferable to hard forks because they allow a smoother transition. Opting for backward-compatible updates when possible facilitates the process and ensures that nodes and miners can adapt without pressure.
6. Continuous Monitoring and Re-evaluation
After an update, it's essential to monitor the network to identify problems or side effects. This continuous process helps ensure cohesion and trust among all participants, keeping Bitcoin as a secure and robust network.
These recommendations, including the use of secure networks for extensive testing, promote a collaborative and secure environment for Bitcoin's consensus process. By adopting a deliberate and strategic approach, stakeholders can preserve Bitcoin's value as a decentralized and censorship-resistant network.
7. Conclusion
Consensus in Bitcoin is more than a set of rules; it's the foundation that sustains the network as a decentralized, secure, and reliable system. Unlike centralized systems, where decisions can be made quickly, Bitcoin requires a much more deliberate and cooperative approach, where the interests of miners, economic nodes, developers, investors, and users must be considered and harmonized. This governance model may seem slow, but it is fundamental to preserving the resilience and trust that make Bitcoin a global store of value and censorship-resistant.
Consensus updates in Bitcoin must balance the need for innovation with the preservation of the network's core principles. The development process of a proposal needs to be detailed and rigorous, going through several testing stages, such as in testnet, signet, and compatible networks like Litecoin and Liquid Network. These networks offer safe environments for proposals to be analyzed and improved before being launched on the main network.
Each proposed change must be carefully evaluated regarding its maturity, impact, backward compatibility, and support among stakeholders. The recommended key questions and appropriate timing are critical to ensure that an update is adopted without compromising network cohesion. It's also essential that the implementation process is continuously monitored and re-evaluated, allowing adjustments as necessary and minimizing the risk of instability.
By following these guidelines, Bitcoin's stakeholders can ensure that the network continues to evolve safely and robustly, maintaining user trust and further solidifying its role as one of the most resilient and innovative digital assets in the world. Ultimately, consensus in Bitcoin is not just a technical issue but a reflection of its community and the values it represents: security, decentralization, and resilience.
8. Links
Whitepaper: https://github.com/bitcoin-cap/bcap
Youtube (pt-br): https://www.youtube.com/watch?v=rARycAibl9o&list=PL-qnhF0qlSPkfhorqsREuIu4UTbF0h4zb
-
-
 @ bf47c19e:c3d2573b
2025-05-12 21:45:41
@ bf47c19e:c3d2573b
2025-05-12 21:45:41Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Definisanje novca
- Šta je sredstvo razmene?
- Šta je obračunska jedinica?
- Šta je zaliha vrednosti?
- Zašto su važne funkcije novca?
- Novac Gubi Funkciju: Alhemičar iz Njutonije
- Eksploatacija pomoću Novca: Agri Perle
- Novac Gubi Funkciju 2. Deo: Kejnslandski Bankar
- Da li nas novac danas eksploatiše?
- Šta je novac, i zašto trebate da brinete?
- Efikasnija Ušteda Novca
- Zasluge
- Molim vas da šerujete!
Google izveštava o stalnom povećanju interesa u svetu za pitanje „Šta je novac?“ koji se postavlja iz godine u godinu, od 2004. do 2021., a sa naglim porastom nakon finansijske krize 2008. godine.
I izgleda se da niko nema dobar odgovor za to.
 Godišnji proseci mesečnih interesa za pretragu. 100 predstavlja najveći interes za pretragu tokom čitavog perioda, koji se dogodio u decembru 2019. Podaci sa Google Trends-a.
Godišnji proseci mesečnih interesa za pretragu. 100 predstavlja najveći interes za pretragu tokom čitavog perioda, koji se dogodio u decembru 2019. Podaci sa Google Trends-a.Međutim, odgovaranje na ovo naizgled jednostavno pitanje pomoći će vam da razjasnite ulogu novca u vašem životu. Jednom kada shvatite kako novac funkcioniše, tačno ćete videti i zašto svet danas ludi – i šta učiniti povodom toga. Zato hajde da se udubimo u to.
Na pitanje šta je novac, većina ljudi otvori svoje novčanike i pokaže nekoliko novčanica – “evo, ovo je novac!”
Ali po čemu se ove novčanice razlikuju od stranica vaše omiljene knjige? Pa, naravno, zavod za izradu novčanica te zemlje je odštampao te novčanice iz vašeg novčanika kako bi se oduprla falsifikovanju, i svi ih koriste da bi kupili odredjene stvari.
Međutim, Nemačka Marka imala je sva ova svojstva u prošlosti – ali preduzeća danas ne prihvataju te novčanice. Zapravo, građani Nemačke su početkom dvadesetih godina prošlog veka spaljivali papirne Marke kako bi grejali svoje domove. Marka je imala veću vrednost kao papir za potpalu nego kao novac!

1923. nemačka valuta poznata kao Marka bila je jeftinija od uglja i drveta!
Pa šta to čini novac, novcem?
Ispostavilo se da ovo nije pitanje na koje je lako dati odgovor.
Definisanje novca
Novac nije fizička stvar poput novčanice dolara. Novac je društveni sistem koji koristimo da bismo olakšali trgovinu robom i uslugama. Međutim, tokom istorije fizička monetarna dobra igrala su ključnu ulogu u društvenom sistemu novca, često kao znakovi koji predstavljaju vrednost u monetarnom sistemu. Ovaj sistem ima tri funkcije: 1) Sredstvo Razmene, 2) Obračunsku Jedinicu i 3) Zalihu Vrednosti.
Odakle dolaze ove funkcije, i zašto su one vredne?
Šta je sredstvo razmene?
Sredstvo razmene je neko dobro koje se obično razmenjuje za drugo dobro. Najčešće objašnjenje za to kako su se pojavila sredstva razmene glasi otprilike ovako: Boris ima ječam i želeo bi da kupi ovcu od Marka. Marko ima ovce, ali želi samo piliće. Ana ima piliće, ali ona ne želi ječam ili ovce.
To se naziva problem sticaja potreba: dve strane moraju da žele ono što druga ima da bi mogle da trguju. Ako se želje dve osobe ne podudaraju, oni moraju da pronađu druge ljude sa kojima će trgovati dok svi ne pronađu dobro koje žele.
 Ljudi koji trguju robom i uslugama moraju da imaju potrebe koje se podudaraju.
Ljudi koji trguju robom i uslugama moraju da imaju potrebe koje se podudaraju.Vremenom, veoma je verovatno da će se određena vrsta robe, poput pšenice, pojaviti kao sredstvo razmene jer su je mnogi ljudi želeli. Uzimajući pšenicu kao primer: pšenica je rešila “sticaje potreba” u mnogim zanatima, jer čak i ako onaj koji prima pšenicu a nije želeo da je koristi za sebe, znao je da će je neko drugi želeti.
Ovo nazivamo prodajnost imovine.
Pšenica je dobar primer dobra za prodaju jer svi moraju da jedu, a od pšenice se pravi hleb. Pšenica ima vrednost kao sastojak hleba i kao dobro koje olakšava trgovinu rešavanjem problema „sticaja potreba“.
Razmislite o svojoj želji da dobijete više novčanica u eurima ili drugoj valuti. Ne možete da jedete novčanice da biste preživeli, a i ne bi vam bile od velike koristi ako poželite da ih koristite kao građevinski materijal za vašu kuću. Međutim, znate da sa tim novčanicama možete da kupite hranu i kuću.
Stvarne fizičke novčanice su beskorisne za vas. Novčanice su vam dragocene samo zato što će ih drugi prihvatiti za stvari koje su vama korisne.
Tokom dugog perioda istorije, novac je evoluirao do te mere da monetarno dobro može imati vrednost, a da to dobro ne služi za bilo koju drugu ‘suštinsku’ upotrebu, poput hrane ili energije. Umesto toga, njegova upotreba je zaliha vrednosti i jednostavna zamena za drugu robu u bilo kom trenutku koji poželite.
Šta jedno dobro čini poželjnijim i prodajnijim od drugog dobra?
Deljivost
Definicija: Sposobnost podele dobra na manje količine.
Loš Primer: Dijamante je teško podeliti na manje komade. Za zajednicu od hiljada ljudi koji dnevno izvrše milione transakcija, dijamanti čine loše sredstvo razmene. Previše su retki i nedeljivi da bi se koristili za mnoge transakcije.
 Potrebno je puno obuke da bi izrezali dijamant.
Potrebno je puno obuke da bi izrezali dijamant.Ujednačenost
Definicija: Sličnost pojedinačnih jedinica odredjenog dobra.
Loš Primer: Krave nisu ujednačene – neke su veće, neke manje, neke bolesne, neke zdrave. Sa druge strane, unca čistog zlata je jednolična – jedna unca je potpuno ista kao sledeća. Ovo svojstvo se takođe često naziva zamenljivost.
 Svaka je jedinstvena na svoj način.
Svaka je jedinstvena na svoj način.Prenosivost
Definicija: Lakoća transporta dobra.
Loš Primer: Krava nije baš prenosiva. Zlatnici su prilično prenosivi. Papirne novčanice su još prenošljivije. Knjiga u kojoj se jednostavno beleži vlasništvo nad tim vrednostima (poput Rai kamenog sistema ili digitalnog bankovnog računa) je neverovatno prenosiva, jer nema fizičkog dobra koje treba nositi sa sobom za kupovinu. Postoji samo sistem za evidentiranje vlasništva nad tim vrednostima u nematerijalnom obliku.
 Novac star 5000 godina VS novac star 13 godina
Novac star 5000 godina VS novac star 13 godinaKako dobro postaje sredstvo razmene?
Dobra postaju, i ostaju sredstva razmene zbog svoje univerzalne potražnje, takođe poznate kao njihova prodajnost, čemu pomažu svojstva koja su gore nabrojana.
Mnogo različitih dobara mogu u različitoj meri delovati kao sredstva razmene u ekonomiji. Danas, naša globalna ekonomija koristi valute koje izdaju države, zlato, pa čak i robu poput nafte kao sredstvo razmene.
Šta je obračunska jedinica?
Stvari se komplikuju kada u ekonomiji postoji mnogo robe koja se prodaje. Čak i sa samo 5 dobara, postoji 10 “kurseva razmene” između svake robe kojih svi u ekonomiji moraju da se sete: 1 svinja se menja za 15 pilića, 1 pile se menja za 15 litara mleka, desetak jaja se menja za 15 litara mleka, i tako dalje. Ako ekonomija ima 50 dobara, među njima postoji 1.225 “kurseva razmene”!
Sredstvo za merenje vrednosti
Zamislite obračunsku jedinicu kao sredstvo za merenje vrednosti. Umesto da se sećamo vrednosti svakog dobra u poredjenju sa drugim dobrima, mi samo treba da se setimo vrednosti svakog dobra u poredjenju sa jednim dobrom – obračunskom jedinicom.
Umesto da se setimo 1.225 kurseva razmene kada imamo 50 proizvoda na tržištu, mi treba da zapamtimo samo 50 cena.
Na primer, ne treba da se sećamo da litar mleka vredi 1/15 piletine ili desetak jaja, možemo da se samo setimo da litar mleka košta 1USD.
 Mnogo opcija, sve u istoj obračunskoj jedinici.
Mnogo opcija, sve u istoj obračunskoj jedinici.Poređenje dobara je lakše sa obračunskom jedinicom
Obračunska jedinica takođe olakšava upoređivanje vrednosti i donošenje odluka. Zamislite da pokušavate da kupite par Nike Air Jordan patika kada ih jedan prodavac prodaje za jedno pile, a drugi za 50 klipova kukuruza.
Šta je zaliha vrednosti?
Do sada smo gledali samo primere transakcija koje se odvijaju u određenom trenutku u vremenu.
Međutim, ljudi vrše transakcije tokom vremena – oni štede novac i troše ga kasnije. Da bi odredjeno dobro moglo da funkcioniše pravilno kao monetarno dobro, ono treba da održi vrednost tokom vremena.
Novac koji vremenom dobro drži vrednost daje njegovom imaocu više izbora kada će taj novac da potroši.
To znači da prodajnost dobra uključuje njegovu sposobnost da održi vrednost tokom vremena.
Šta jedno dobro čini boljom zalihom vrednosti od drugog dobra?
Trajnost
Definicija: Sposobnost dobra da vremenom zadrži svoj oblik.
Loš Primer: Jagode čine lošu zalihu vrednosti jer se lako oštete i brzo trunu.
Odluka je daleko lakša ako jedan prodavac naplaćuje 150 USD, a drugi 200 USD – odmah je očigledno koja je bolja ponuda jer su vrednosti izražene u istoj jedinici.
 Nije sjajna forma novca.
Nije sjajna forma novca.Teške za Proizvodnju
Definicija: Teškoće koje ljudi imaju u proizvodnji veće količine dobra.
Loš Primer: Papirne novčanice predstavljaju lošu zalihu vrednosti jer banke i vlade mogu jeftino da ih naprave.
Sa zlatom je suprotno – u ponudi se nalazi ograničena količina uprkos velikoj potražnji za njim, jednostavno zato što ga je vrlo teško iskopati iz zemlje. Ova ograničena ponuda osigurava da svaka jedinica zlata održi vrednost tokom vremena.
 Traženje zlata je spora i teška aktivnost. Obično se ne pronađe puno!
Traženje zlata je spora i teška aktivnost. Obično se ne pronađe puno!Kako dobra postaju zalihe vrednosti?
Dobro postaje zaliha vrednosti ako se vremenom pokaže trajnim i teškim za proizvodnju.
Samo će vreme pokazati da li je neko dobro zaista trajno i da li ga je teško proizvesti. Zbog toga neki oblici novca su postojali vekovima pre nego što je neko otkrio način da ih proizvede više, i na kraju se to dobro više nije koristilo kao novac.
Ovo je priča o školjkama, Rai kamenju i mnogim drugim oblicima novca tokom istorije.
Zlato je primer dobra koje je hiljadama godina služilo kao dobra zaliha vrednosti. Zlato se ne razgrađuje tokom vremena i još uvek ga je teško proizvesti. Hiljadama godina alhemičari su bezuspešno pokušavali da sintetišu zlato iz jeftinih materijala.
Čak i sa današnjim naprednim rudarskim tehnikama, svake godine svi svetski rudnici zlata zajedno mogu da proizvedu samo 2% od ukupne ponude zlata u prometu.
Teškoće u proizvodnji zlata daju izuzetno visok odnos “zaliha i protoka”: zaliha je broj postojećih jedinica, a protok su nove jedinice stvorene tokom određenog vremenskog perioda. Svake godine se stvori vrlo malo novih jedinica zlata, iako je potražnja za zlatom obično vrlo velika.
Kombinujući ovo sa deljivošću, ujednačenošću i prenosivošću zlata, nije ni čudo što je zlato čovečanstvu služilo kao monetarno dobro tokom poslednjih 5.000 godina. Pošto je zlato teško proizvesti, možemo ga nazvati teškim novcem (hard money).
Kao rezultat toga, svoju vrednost je u velikoj meri zadržao kroz milenijume. Cena većine dobara i usluga u pogledu zlata zapravo se vremenom smanjivala kao rezultat tehnoloških inovacija, koje sve proizvode čine jeftinijim.
Uzmimo na primer cene hrane prema praćenju Kancelarije za hranu i poljoprivredu UN-a: sa obzirom na skokove u poljoprivrednoj tehnologiji tokom poslednjih 60 godina, cene hrane drastično su pale kada se procenjuju u zlatu. To čak i važi uprkos činjenici da obični ljudi retko koriste zlato za kupovinu stvari.
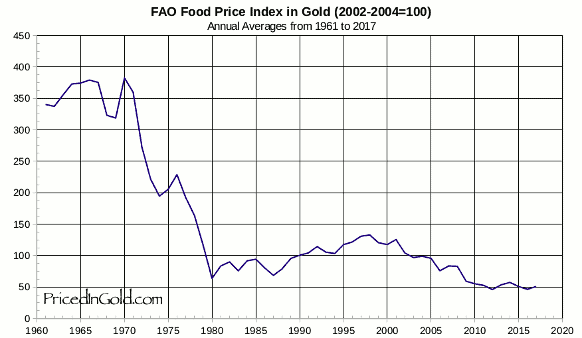 Cene hrane su padale u pogledu zlata tokom proteklih 60 godina, i mnogo pre toga (FAO Indeks Cena Hrane u Zlatu)
Cene hrane su padale u pogledu zlata tokom proteklih 60 godina, i mnogo pre toga (FAO Indeks Cena Hrane u Zlatu)Zaliha vrednosti omogućava ljudima da uštede novac kako bi mogli da ga ulažu u pokretanje preduzeća i obrazovanje, povećavajući produktivnost društva.
Monetarna dobra koja dobro čuvaju vrednost takođe podstiču dugoročniji pogled na život, ili kratke vremenske preference. Pojedinac može da radi 10 godina, uštedi odredjeno monetarno dobro koje je dobra zaliha vrednosti, i nema potrebe da se plaši da će njegova ušteđevina biti izbrisana krahom tržišta ili povećanjem ponude tog dobra.
Zašto su važne funkcije novca?
Kada neki oblik novca izgubi bilo koju od svojih važnih funkcija kao što su sredstvo razmene, obračunska jedinica i zaliha vrednosti, celokupna ekonomija i društvo mogu da se rastrgnu.
Tokom istorije često vidimo grupe ljudi koje eksploatišu druge iskorišćavajući nesporazume o novcu i važnosti njegovih funkcija.
Sledeće, proći ću kroz istoriju novca, prvo hipotetički da bih ilustrovao poentu, a zatim ću preći na stvarne istorijske primere. Kroz ove primere videćemo štetne efekte na društva u slučajevima kada se izgubi samo jedna od tih ključnih funkcija novca.
Novac Gubi Funkciju: Alhemičar iz Njutonije
Kroz istoriju, mnoga dobra su dolazila i odlazila kao oblici novca. Na žalost, kada se neki oblik novca ukine, ponekad postoji grupa ljudi koja eksploatiše drugi oblik manipulišući tim novcem.
Hajde da pogledamo hipotetičko selo zvano Njutonija da bismo razumeli kako dolazi do ove eksploatacije.
Zelene perle postaju Novac
Tokom stotina godina ribolova u obližnjoj reci, stanovnici Njutonije sakupljali su zelene perle iz vode. Zrnca su mala, lagana, izdržljiva, jednolična i retko se pojavljuju u reci. Ljudi prvo priželjkuju perle zbog svoje lepote. Na kraju, seljani shvataju da svi drugi žele perle – one se vrlo lako mogu prodati. Zrnca uskoro postaju sredstvo razmene i obračunska jedinica u selu: pile je 5 zrna, vreća jabuka 2 zrna, krava 80 zrna.
Ukupna ponuda perli je prilično konstantna i cene se vremenom ne menjaju mnogo. Seoski starešina je uveren da može da se opustiti u poslednjim danima živeći od svoje velike zalihe perli.
Alhemičar stvara više perli
Seoski alhemičar je poželeo da bude bogat čovek, ali nije voleo da vredno radi na tome. Umesto da traži perle u reci ili da prodaje vrednu robu drugim seljanima, on sedeo je u svojoj laboratoriji. Na kraju je otkrio kako da lako stvori stotine perli sa malo peska i vatre.
Seljani koji su tragali za perlama u reci bili su srećni ako bi svaki dan pronašli po 1 zrno. Alhemičar je mogao da proizvede stotine uz malo napora.
Alhemičar troši svoje perle
Budući da je bio prilično zao, alhemičar nije svoj metod pravljenja zrna delio ni sa kim drugim. Stvorio je sebi još više perli i počeo da ih troši za dobra na tržištu u Njutoniji. Tokom sledećih meseci, alhemičar je kupio farmu pilića, nekoliko krava, finu svilu, posteljine i ogromno imanje. On je imao priliku da kupi ova dobra po normalnim cenama na tržištu.
Alhemičarevo trošenje ostavljalo je seljanima mnogo perli, ali malo njihove vredne robe.
Svi seljani su se osećali bogatima – imali su tone perli! Međutim, polako su primetili da i svi ostali takodje imaju tone.
Cene počinju da rastu
Uzgajivač pilića primetio je da sva roba koju je trebalo da kupi na pijaci poskupela. Džak jabuka sada se prodaje za 100 perli – 50 puta više od njihove cene pre nekoliko meseci!
Iako je sada imao hiljade perli, uskoro bi mogao da ostane bez njih zbog ovih cena. Pitao se – da li zaista može sebi da priušti da prodaje svoje piliće za samo 5 perli po komadu? Morao je i on da podigne svoje cene.
Jednostavno rečeno, kao rezultat alhemičarevog trošenja njegovih novostvorenih perli, bilo je previše perli koje su jurile premalo dobara – pa su cene porasle.
Kupci robe bili su spremni da potroše više perli da bi kupili potrebna dobra. Prodavci robe su trebali da naplate više da bi bili sigurni da su zaradili dovoljno da kupe potrebna dobra za sebe.
Budući da su cene svih dobara porasle, možemo reći da se vrednost svake perle smanjila.
Nejednakost bogatstva raste
Seoski starešina, koji je vredno radio da sačuva hiljade perli, sada se našao osiromašenim i gladnim. U međuvremenu, alhemičar je udobno sedeo na svom velikom imanju sa kravama, pilićima i slugama koji su se brinuli za svaki njegov hir.
Alhemičar je efikasno ukrao bogatstvo celog sela, tako što je jeftino proizvodio perle i koristio ih za kupovinu vredne robe.
Ono što je najvažnije, kupio je robu pre nego što je tržište shvatilo da je više perli u opticaju i da ima manje robe, što je dovelo do rasta cena. Ova dodatna proizvodnja perli nije dodala korisnu robu ili usluge selu. Kroz istoriju, mnoga dobra su dolazila i odlazila kao oblici novca. Na žalost, kada se neki oblik novca ukine, ponekad postoji grupa ljudi koja eksploatiše drugi oblik manipulišući tim novcem.
Hajde da pogledamo hipotetičko selo zvano Njutonija da bismo razumeli kako dolazi do ove eksploatacije.
Zelene perle postaju Novac
Tokom stotina godina ribolova u obližnjoj reci, stanovnici Njutonije sakupljali su zelene perle iz vode. Zrnca su mala, lagana, izdržljiva, jednolična i retko se pojavljuju u reci. Ljudi prvo priželjkuju perle zbog svoje lepote. Na kraju, seljani shvataju da svi drugi žele perle – one se vrlo lako mogu prodati. Zrnca uskoro postaju sredstvo razmene i obračunska jedinica u selu: pile je 5 zrna, vreća jabuka 2 zrna, krava 80 zrna.
Ukupna ponuda perli je prilično konstantna i cene se vremenom ne menjaju mnogo. Seoski starešina je uveren da može da se opustiti u poslednjim danima živeći od svoje velike zalihe perli.
Alhemičar stvara više perli
Seoski alhemičar je poželeo da bude bogat čovek, ali nije voleo da vredno radi na tome. Umesto da traži perle u reci ili da prodaje vrednu robu drugim seljanima, on sedeo je u svojoj laboratoriji. Na kraju je otkrio kako da lako stvori stotine perli sa malo peska i vatre.
Seljani koji su tragali za perlama u reci bili su srećni ako bi svaki dan pronašli po 1 zrno. Alhemičar je mogao da proizvede stotine uz malo napora.
Alhemičar troši svoje perle
Budući da je bio prilično zao, alhemičar nije svoj metod pravljenja zrna delio ni sa kim drugim. Stvorio je sebi još više perli i počeo da ih troši za dobra na tržištu u Njutoniji. Tokom sledećih meseci, alhemičar je kupio farmu pilića, nekoliko krava, finu svilu, posteljine i ogromno imanje. On je imao priliku da kupi ova dobra po normalnim cenama na tržištu.
Alhemičarevo trošenje ostavljalo je seljanima mnogo perli, ali malo njihove vredne robe.
Svi seljani su se osećali bogatima – imali su tone perli! Međutim, polako su primetili da i svi ostali takodje imaju tone.
Cene počinju da rastu
Uzgajivač pilića primetio je da sva roba koju je trebalo da kupi na pijaci poskupela. Džak jabuka sada se prodaje za 100 perli – 50 puta više od njihove cene pre nekoliko meseci!
Iako je sada imao hiljade perli, uskoro bi mogao da ostane bez njih zbog ovih cena. Pitao se – da li zaista može sebi da priušti da prodaje svoje piliće za samo 5 perli po komadu? Morao je i on da podigne svoje cene.
Jednostavno rečeno, kao rezultat alhemičarevog trošenja njegovih novostvorenih perli, bilo je previše perli koje su jurile premalo dobara – pa su cene porasle.
Kupci robe bili su spremni da potroše više perli da bi kupili potrebna dobra. Prodavci robe su trebali da naplate više da bi bili sigurni da su zaradili dovoljno da kupe potrebna dobra za sebe.
Budući da su cene svih dobara porasle, možemo reći da se vrednost svake perle smanjila.
Nejednakost bogatstva raste
Seoski starešina, koji je vredno radio da sačuva hiljade perli, sada se našao osiromašenim i gladnim. U međuvremenu, alhemičar je udobno sedeo na svom velikom imanju sa kravama, pilićima i slugama koji su se brinuli za svaki njegov hir.
Alhemičar je efikasno ukrao bogatstvo celog sela, tako što je jeftino proizvodio perle i koristio ih za kupovinu vredne robe.
Ono što je najvažnije, kupio je robu pre nego što je tržište shvatilo da je više perli u opticaju i da ima manje robe, što je dovelo do rasta cena. Ova dodatna proizvodnja perli nije dodala korisnu robu ili usluge selu.
Eksploatacija pomoću Novca: Agri Perle
Nažalost, priča o alhemičaru iz Njutonije nije u potpunosti hipotetička. Ovaj prenos bogatstva kroz stvaranje novca ima istorijske i moderne presedane.
Na primer, afrička plemena su nekada koristila staklene perle, poznate kao “agri perle”, kao sredstvo razmene. U to vreme plemenskim ljudima je bilo veoma teško da prave staklene perle, i one su predstavljale težak novac unutar njihovog plemenskog društva.
Niko nije mogao jeftino da proizvede perle i koristiti ih za kupovinu skupe, vredne robe poput kuća, hrane i odeće.
Eksploatacija pomoću Novca: Agri Perle
Nažalost, priča o alhemičaru iz Njutonije nije u potpunosti hipotetička. Ovaj prenos bogatstva kroz stvaranje novca ima istorijske i moderne presedane.
Na primer, afrička plemena su nekada koristila staklene perle, poznate kao “agri perle”, kao sredstvo razmene. U to vreme plemenskim ljudima je bilo veoma teško da prave staklene perle, i one su predstavljale težak novac unutar njihovog plemenskog društva.
Niko nije mogao jeftino da proizvede perle i koristiti ih za kupovinu skupe, vredne robe poput kuća, hrane i odeće.
 Perle proizvedene u Gani
Perle proizvedene u GaniSve se promenilo kada su stigli Evropljani, i primetili upotrebu staklenih perli kao novca.
U to vreme, Evropljani su mogli jeftino da stvaraju staklo u velikim količinama. Kao rezultat toga, Evropljani su počeli tajno da uvoze perle i koriste ih za kupovinu dobara, usluga i robova od Afrikanaca.
 Peć za izradu stakla u Muranu, Italija. Ovo ostrvo izvan Venecije proizvodi staklo od 15. veka.
Peć za izradu stakla u Muranu, Italija. Ovo ostrvo izvan Venecije proizvodi staklo od 15. veka.Vremenom se iz Afrike izvlačila vredna roba i ljudi, dok je plemenima ostajalo mnogo perli i malo robe.
Perle su izgubile veći deo vrednosti zbog inflacije uzrokovane snabdevanjem od strane Evropljana.
Rezultat je bio osiromašenje afričkih plemena i bogaćenje Evropljana, kako to ovde objašnjava monetarni istoričar Bezant Denier.
Dragocena roba je kupljena jeftino proizvedenim monetarnim dobrom.
Profitiranje na proizvodnji novca: Emisiona dobit
Ova priča ilustruje kako se bogatstvo prenosi kada jedna grupa može jeftino da proizvodi monetarno dobro.
Razlika između troškova proizvodnje monetarnog dobra i vrednosti tog monetarnog dobra poznata je kao emisiona dobit, eng. seignorage.
Kada je monetarno dobro mnogo vrednije od troškova proizvodnje, ljudi će proizvesti više od monetarnog dobra da bi uhvatili profit od emisione dobiti.
Na kraju će ova povećana ponuda dovesti do pada vrednosti monetarnog dobra. To je zbog zakona ponude i potražnje: kada se ponuda povećava, cena (poznata i kao vrednost) dobra opada.
Novac Gubi Funkciju 2. Deo: Kejnslandski Bankar
U priči o Njutoniji, alhemičar je otkrio način da se od malo peska jeftino stvori više zelenih perli. To se u stvarnosti odigralo kroz trgovinu između Evropljana i Afrikanaca, pričom o agri perlama. Međutim, ove priče su pomalo zastarele – mi više ne trgujemo robom za perle.
Da bismo nas doveli do modernog doba, hajde da promenimo neka imena u našoj priči:
- Selo Njutonija postaje država koja se zove Kejnsland
- Alhemičar postaje bankar
- Seoski starešina postaje penzioner
- Zelene perle postaju zlato, koje niko ne može jeftinije da stvori – čak ni bankar.
Bankar Menja Papirne Novčanice za Zlato
Kao i u stvarnosti, bankar u ovoj priči nema formulu ili trik da stvori više zlata. Međutim, bankar bezbedno čuva zlato u vlasništvu svakog građanina Kejnslanda. Bankar daje svakom građaninu po jednu potvrdu za svaku uncu zlata koje ima u svom trezoru.
Te potvrde se mogu iskoristiti u bilo koje vreme za stvarno zlato. Papirne potvrde ili novčanice su mnogo pogodnije za plaćanje nego nošenje zlata kroz supermarket.
Građani su srećni – oni imaju prikladno sredstvo plaćanja u vidu bankarevih novčanica, i znaju da niko ne može da ukrade njihovo bogatstvo falsifikujući više zlata.
Građani na kraju počinju da plaćaju u potpunosti papirnim novčanicama, ne trudeći se nikad da zamene svoje novčanice za zlato. Na kraju, novčanice postaju “dobre kao i zlato” – svaka predstavlja fiksnu količinu zlata u bankarevom trezoru.
Ukupno kruži 1.000.000 novčanica, od kojih je svaka otkupljiva za jednu uncu zlata. 1.000.000 unci zlata sedi u bankarevom trezoru. Svaka novčanica je u potpunosti podržana u zlatu.
Starešina koji je sačuvao sve svoje perle u priči o Njutoniji sada je penzioner u Kejnslandu, koji svoje zlato drži u banci i planira da ugodno živi od novčanica koje je dobio zauzvrat.
Hajde da u ovu priču dodamo i novi lik: premijera Kejnslanda. Premijer naplaćuje porez od građana i koristi ga za plaćanje javnih usluga poput policije i vojske. Premijer takođe drži vladino zlato kod bankara.
Bankar Menja Papirne Novčanice za Dug
Premijer želi da osigura da nacionalno zlato ostane na sigurnom, pa banku štiti policijom. Bankar i premijer se zbog toga zbližavaju, pa premijer traži uslugu. Traži od bankara da kreira 200.000 novčanica za premijera, uz obećanje da će mu premijer vratiti za pet godina. Premijeru su novčanice potrebne za finansiranje rata. Građani Kejnslanda borili su se protiv većih poreza zbog finansiranja rata, pa je morao da se obrati bankaru.
Bankar se slaže da izradi novčanice, ali pod jednim uslovom: bankar uzima deo od 10.000 novčanica za sebe. Premijer prihvata posao kojim bankar ’kupuje državni dug’. Sada je u opticaju 1.200.000 novčanica, potpomognutih kombinacijom 1.000.000 unci zlata i ugovorom o dugu sa vladom za 200.000 novčanica.
Premijer troši svoje nove novčanice na bombe kupujući ih od dobavljača iz domaće vojne industrije, a bankar sebi kupuje veliki luksuzni stan.
Dobavljač iz vojne industrije koristi sve nove novčanice koje je dobio od premijera da kupi amonijum nitrat (đubrivo koje se koristi u bombama) za proizvodnju bombi. Sve njegove kupovine povećavaju cenu đubriva za uzgajivače pšenice u Kejnslandu, pa oni podižu cenu pšenice.
Kao uzrok toga, pekar koji kupuje pšenicu treba da podigne cenu svog hleba da bi ostao u poslu. Na taj način cene u Kejnslandu počinju da rastu, baš kao što su to činile u Njutoniji kada su nove perle ušle u opticaj.
Papirne Novčanice Više Ne Predstavljaju Zlato
Penzioner nailazi na finansijski časopis u kojem se pominje premijerov dogovor da se zaduži za finansiranje rata. Obzirom da je mudar, on zna da bombe loše vraćaju ulaganje i sumnja da će premijer ikada da vrati svoj dug.
Ako on ‘podmiri’ svoj dug, to bi ostavilo 1.200.000 novčanica u opticaju sa samo 1.000.000 unci zlata da bi ih podržalo, obezvređujući njegovu ušteđevinu. Već oseća stisak u džepu zbog porasta cena, i on odlučuje da se uputi u lokalnu banku i preda svoje novčanice i zameni ih za zlato, koje niko ne može da napravi u većoj količini.
Kada penzioner stigne u banku, on zatiče i mnoge druge okupljene oko banke. Svi oni se nadaju da će uzeti zlato koje predstavljaju njihove novčanice. Građani Kejnslanda sa pravom se plaše da njihove novčanice gube na vrednosti – oni to već osećaju zbog porasta cena.
Vrata su zaključana, sa obaveštenjem bankara na njima:
Po nalogu premijera, onom koji se plaši za stabilnost ove bankarske institucije, ova banka više neće podržavati konvertibilnost papirnih novčanica u zlato. Hvala vam!
Gomila se razilazi, ostavljena sa jednim izborom: da zadrže svoje novčanice, koje sada vrede manje od 1 unce zlata. Građani sa dovoljno finansijske stabilnosti odlučuju da ulože svoje novčanice u kupovinu akcija banke i kompanija vojne industrije, koje dobro posluju jer mogu da kupuju stvari pre nego što se povećaju tržišne cene.
Mnogi ljudi nisu u mogućnosti da investiraju – oni moraju da gledaju kako njihove zarade stagniraju i kako njihova ušteđevina polako ali sigurno gubi vrednost.
Penzioner, koji se nadao da će živeti od novčanica koje je zaradio tokom svojih 40 radnih godina, sada 40 sati nedeljno provodi iza kase u lokalnoj prodavnici, pitajući se gde je sve pošlo po zlu.
Dug Nikada Nije Otplaćen
Prošlo je nekoliko godina, a premijerov dug prema banci dolazi na naplatu. Budući da je potrošio svih 200.000 novčanica na bombe, koje nemaju baš dobar povraćaj ulaganja, on nema novčanice koje može da vrati banci. Plus, premijer želi da kupi još bombi za svoj rat.
Bankar uverava premijera da je sve u redu. Bankar će napraviti novi ugovor o dugu za 600.000 novčanica, koji bi trebao da stigne na naplatu u narednih 5 godina. Premijer može da iskoristi 200.000 od tih novih 600.000 novčanica da vrati svoj prvobitni dug prema banci, zadrži još 300.000 da kupi još bombi i da 100.000 bankaru da bi mu platio njegove usluge.
To nastavlja da se dešava – svaki put kada dug dospeva na naplatu, bankar stvara više novčanica za vraćanje starijih dugova i daje premijeru još više novca za trošenje. Ovaj ciklus se nastavlja.
Šta se dešava u Kejnslandu?
- Oni koji prvi dobiju nove novčanice, gledaju kako se njihovo bogatstvo povećava
- To uključuje bankara, premijera, vladu i sve one koji mogu da pristupe mogućnostima za investiranje u preduzeća koja prva dobiju nove novčanice (finansijske, vojne itd.).
- Cene roba rastu
- Cene se ne povećavaju ravnomerno – one se povećavaju gde god nove novčanice prvo uđu u ekonomiju i od tog trenutka imaju efekat talasa na tržišta. U našem primeru prvo raste cena amonijum nitrata, zatim cena pšenice, pa cena hleba. A tek na kraju zarade običnih ljudi.
- Štednja i životni standard opšte populacije se smanjuju
- Najviše pate oni koji žive od plate do plate i ne mogu da ulažu. Čak i oni koji su u mogućnosti da investiraju podložni su hirovima tržišta. Mnogi su prisiljeni da prodaju svoje investicije po niskim cenama tokom pada tržišta samo da bi platili svoje dnevne potrebe.
- Razlika u prihodima i bogatstvu između bogatih i siromašnih se povećava
- Bogatstvo opšte populacije se smanjuje, dok se bogatstvo onih koji su blizu mesta gde se troše nove novčanice povećava. Rezultat je disparitet koji se vremenom samo proširuje.
Da li nas novac danas eksploatiše?
Priča o Njutoniji i stvarna priča o agri perlama u Africi deluju pomalo zastarelo. Priča o Kejnslandu, međutim, deluje neobično poznato. U našem svetu cene robe uvek rastu, i vidimo rekordne nivoe nejednakosti u bogatstvu.
U poslednjem odeljku ovog našeg članka Šta je novac, proći ću kroz nastanak bankarstva i korake koji su bili potrebni da se dođe do današnjeg sistema, gde banke i vlade sarađuju u kontroli ekonomije i samog novca.
Šta su banke, i odakle su one došle?
Pojava bankarstva verovatno se dogodila da bi olakšala poljoprivrednu trgovinu i da bi povećala pogodnosti. Iako su se mnoga društva na kraju konvergirala ka upotrebi zlata i srebra kao novca, ovi metali su bili teški i opasni za nošenje kao tovar. Međutim, u mnogim slučajevima ih nije ni trebalo prevoziti. Uzmite ovaj primer:
Grad treba da plati poljoprivrednicima na selu za žito, a poljoprivrednici gradskoj vojsci za zaštitu od varvara. U ovom dogovoru zlato se kreće u oba smera: prema poljoprivrednicima u selu kako bi im se platilo žito, i nazad u grad da bi se platila vojska. Da bi olakšali ove transakcije, preduzetnici su stvorili koncept banke. Banka je zlato čuvala u sigurnom trezoru i izdavala novčanice od papira. Svaka priznanica je predstavljala potvrdu da njen imaoc poseduje određenu količinu zlata u banci. Imaoc novčanice je u svako doba mogao da uzme svoje zlato nazad vraćanjem te novčanice banci.
Korisnici banke mogli su lakše da trguju sa novčanicama od papira, i onaj koji poseduje novčanice mogao je da preuzme njihovo fizičko zlato u bilo kom trenutku. To je te novčanice učinilo “dobrim kao i zlato”.
Banke su izdržavale svoje poslovanje naplaćujući od kupaca naknadu za skladištenje zlata ili pozajmljivanjem dela zlata i zaračunavanjem kamata na njega. Trgovina na ovaj način je mogla da se odvija sa laganim novčanicama od papira umesto sa teškim vrećama zlatnika.
Ovakva praksa sa transakcijama, korišćenjem papirne valute potpomognute monetarnim dobrima, verovatno je započela u Kini u 7. veku.
Na kraju se proširila Evropom 1600-ih, a svoj zalet dobila je u Holandiji sa bankama poput Amsterdamske Wisselbanke. Novčanice Wisselbank-e često su vredele više od zlata koje ih je podržavalo, zbog dodane vrednosti njihovih pogodnosti.
Uspon nacionalnih ‘centralnih banaka’
Tokom vekova, zlato je počelo da se sakuplja u trezorima banaka, jer su ljudi više voleli pogodnosti transakcija sa novčanicama.
Na kraju, nacionalne banke u vlasništvu vlada preuzele su ulogu čuvanja zlata od privatnih banaka koje su započeli preduzetnici.
Nacionalne papirne valute potpomognute zlatnim rezervama u nacionalnim bankama zamenile su novčanice iz privatnih banaka. Sve nacionalne valute bile su jednostavno potvrde za zlato koje se nalazilo u trezoru nacionalne banke.
Ovaj sistem je poznat kao zlatni standard – sve valute su jednostavno predstavljale različite težine zlata.
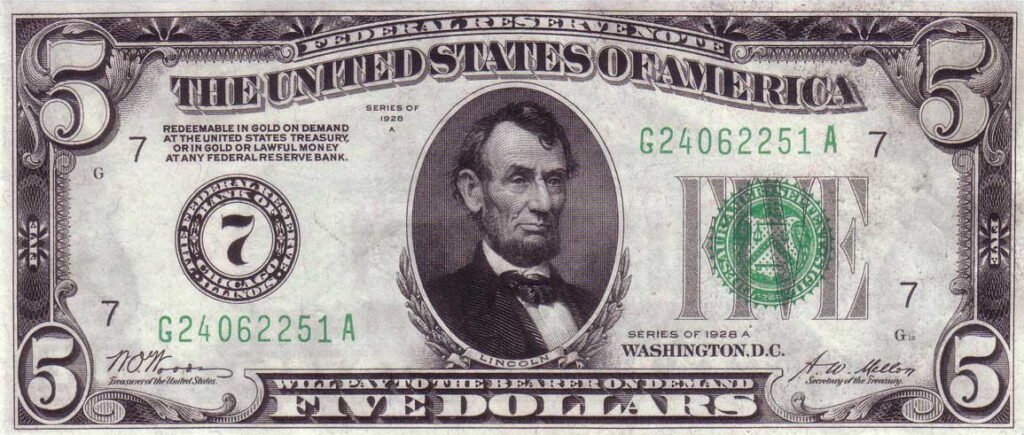 U gornjem levom uglu novčanice možete videti da piše da je novčanica “zamenljiva za zlato”. Savremeni dolari nemaju ovaj natpis, ali inače izgledaju vrlo slično. Izvor
U gornjem levom uglu novčanice možete videti da piše da je novčanica “zamenljiva za zlato”. Savremeni dolari nemaju ovaj natpis, ali inače izgledaju vrlo slično. IzvorZlatni sistem je postojao veći deo vremena, sve do Prvog svetskog rata. Vladama je bilo teško da prikupe novac za ovaj rat putem poreza, pa su morale da budu kreativne.
Kada vlade troše više nego što zarađuju na porezima, to se naziva deficitna potrošnja.
Kako vlade mogu ovo da urade? Vlade to rade tako što pozajmljuju novac prodavajući svoj dug.
Tokom Prvog svetskog rata, vlade su građanima i preduzećima prodavale vrstu duga koja se naziva ratna obveznica. Kada građanin kupi ratnu obveznicu, on preda svoj novac vladi i dobije papir u kojem je stajalo vladino obećanje da će vlasniku obveznice vratiti novac, plus kamate, za nekoliko godina.
 Plakat koji obaveštava građane, tražeći od njih da kupe ratne obveznice – što predstavlja zajam vladi. Izvor
Plakat koji obaveštava građane, tražeći od njih da kupe ratne obveznice – što predstavlja zajam vladi. IzvorCentralne banke ‘monetizuju’ državni dug
Međutim, građani i preduzeća nisu bili voljni da kupe dovoljno ratnih obveznica za finansiranje Prvog svetskog rata.
Vlade se nisu predale – pa su zatražile od svojih nacionalnih ‘centralnih banaka’ da one kupe ove obveznice. Centralne banke su otkupile obveznice, ali ih nisu platile valutom potpomognutom postojećim zlatnim rezervama, kao što su to činili građani i banke prilikom kupovine obveznica.
Centralne banke su umesto toga davale vladi novu, sveže štampanu papirnu valutu potpomognutu samo obveznicom. Ovu valutu podržalo je samo obećanje da će im vlada vratiti dugove. Ovo je poznato kao monetizacija duga.
Budući da su ratne obveznice i valuta samo komadi papira, one su lake i jeftine za proizvodnju i mogu se napraviti u ogromnim količinama. Ono što ograničava proizvodnju i jednog i drugog je poverenje.
Ima smisla da se neko rastane od svog teško stečenog novca da kupi državnu obveznicu, samo ako veruje da će vlada da vrati svoj dug, plus kamate. Centralna banka je “krajnji kupac”, što znači da će ona da kupi državne obveznice kada to niko drugi neće da uradi.
Zapamtite, centralnu banku gotovo da ništa ne košta da kupi državne obveznice, jer oni sami štampaju valutu da bi ih kupili.
Zamislite da pridjete najskupljem automobilu u autosalonu – koji košta 100.000 USD. Mislite da je automobil lep, ali taj novac biste radije potrošili na lepši stan – tako da ste spremni da platite samo 40.000 USD za taj auto.
Sada, hajde da zamislimo da imate štampač za novac i da vas košta samo 50 USD za mastilo i papir da bi ištampali 1.000.000 USD. Vi biste odmah kupili auto, čak i ako biste morali da se cenkate sa drugim čovekom, i da ga na kraju platite 150.000 USD!
Ista stvar se dešava kada centralna banka kupuje obveznice (dugove) od vlade. Centralna banka može da stvori valutu toliko jeftino, da su spremni da plate i više nego što bi drugi platili ove obveznice i nastaviće da ih kupuju čak i kada niko drugi ne bude želeo.
Monetizacija duga uzrokuje inflaciju
Kada centralne banke monetizuju državni dug, funkcija novca kao zalihe vrednosti počinje da se nagriza. Vlada troši novi novac koji je dobila od svoje centralne banke na ratnu robu, obroke i još mnogo toga.
Cene roba rastu od ove novoštampane valute koja kruži kroz ekonomiju. Kada se cene povećavaju, to znači da se vrednost svake jedinice valute smanjuje. Svi koji drže valutu sada imaju manje vrednosti. Danas to nazivamo sporim gubitkom funkcije zalihe vrednosti u novčanoj inflaciji.
Za Nemačku nakon Prvog svetskog rata monetizacija duga izazvala je totalni slom Nemačke ekonomije i stvorila uslove za rast fašizma.
Kao deo sporazuma o prekidu vatre koji je okončao Prvi svetski rat, Nemačka je pobednicima morala da plati ogroman novac. Nemačkoj vladi je bio preko potreban novac, pa su prodale obveznice (dug) Rajhsbanci, nemačkoj centralnoj banci.
Ovaj postupak doveo je do toga da je vlada štampala toliko maraka (tadašnja nemačka valuta) da je tempo inflacije u Nemačkoj ubrzan u hiperinflaciju početkom 1920-ih. Cena vekne hleba za samo 4 godine popela se sa 1,2 marke na 428 biliona maraka.
Tokom i posle Prvog svetskog rata, SAD, Britanija, Francuska i mnoge druge vlade pratile su Nemačku u štampanju valute potpomognute državnim dugom.
To je dovelo do toga da su građani želeli da svoju papirnu valutu zamene za zlato, baš kao i penzioner iz priče o Kejnslandu.
Međutim, mnoge vlade su suspendovale konvertibilnost svojih valuta u zlato. Ovim potezom vlade su primorale svoje građane da drže nacionalnu papirnu valutu i gledaju kako se njihova ušteda smanjuje u vrednosti.
Da bi mogle da nastave da štampaju novac i da bi ga trošile na nepopularne programe za koje nisu mogle da skupljaju poreze za finansiranje – poput ratova.
Bretton Woods: Novi monetarni sistem
Nakon razaranja koja su donela dva svetska rata, vlade su uspostavile novi globalni monetarni sistem prema Bretton Woods-ovom sporazumu iz 1944. godine.
Prema ovom sporazumu, valuta svake države konvertovala se po fiksnom kursu sa američkim dolarom. Američki dolar je zauzvrat predstavljao zlato po stopi od 35 USD za jednu trojsku uncu zlata*.
Sve globalne valute su stoga još uvek bile jednostavna reprezentacija zlata, putem američkih dolara kao posrednika. Redovni građani više nisu mogli da otkupljuju svoje valute za zlato iz Sjedinjenih Država. Međutim, strane centralne banke mogle bi da dođu u Sjedinjene Države da bi zamenile dolare za zlato po stopi od 35 USD za jednu uncu zlata.
Međutim, vlada Sjedinjenih Država nije uvek držala dovoljno zlata da podrži sve dolare u opticaju. Američka vlada nastavila je da finansira proširene socijalne i vojne programe prodajom državnog duga svojoj centralnoj banci, Federalnim rezervama, koja je povećala ponudu dolara bez povećanja ponude zlata koja podupire te dolare.
*Trojna unca je standardna mera čistog zlata i ima malo veću težinu od normalne unce.
Propast Bretton Woods-a
Tokom 1970-ih, sve veći troškovi rata u Vijetnamu i stranih vlada koje su otkupljivale svoje dolare za zlato, stvorili su pritisak na Trezor Sjedinjenih Država.
Ponuda dolara je porasla, dok je zlato u posedu Sjedinjenih Država opalo. Od 1950. pa do početka 1970-ih, rezerve zlata koje je držala vlada Sjedinjenih Država smanjile su se za više od 50%, sa 20 metričkih tona na samo 8 metričkih tona.
Godine 1970. država je imala zlata u vrednosti od samo 12 biliona dolara po zvaničnom kursu od 35 dolara za trojsku uncu zlata. Tokom ovog istog vremenskog perioda, ukupna ponuda američkih dolara otišla je sa oko 32 biliona USD na skoro 70 biliona USD.
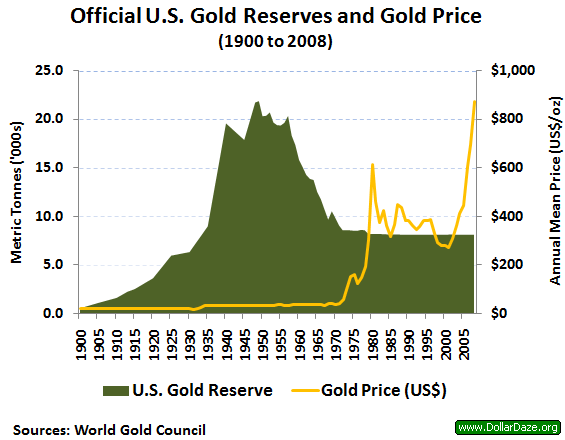 Zvanične rezerve zlata u SAD-u su naglo padale od 1950. do 1970. godine, dok su se dolari u opticaju povećavali. Izvor: Wikipedia, DollarDaze.org
Zvanične rezerve zlata u SAD-u su naglo padale od 1950. do 1970. godine, dok su se dolari u opticaju povećavali. Izvor: Wikipedia, DollarDaze.orgAmerička vlada nije bila u stanju da potkrepi dolare zlatom od 35 dolara po trojnoj unci, što dovelo do rizika za čitav globalni monetarni sistem.
Početkom sedamdesetih godina, trojna unca zlata trebala je da vredi 200 USD da bi u potpunosti podržala sve američke dolare u opticaju. Rečeno na drugi način, Sjedinjene Države su pokušavale da kažu svetu da jedan dolar vredi 1/35 trojne unce zlata, ali u stvarnosti dolar je vredeo samo 1/200 trojne unce.
Kad su strane vlade trebale da pribave dolare za međunarodnu trgovinu i rezerve, bile su opelješene. Francuska vlada je to shvatila šezdesetih godina prošlog veka i počela je da prodaje svoje američke dolare za zlato po zvaničnom kursu od 35 dolara za trojsku uncu zlata.
Zemlje su počinjale da se bude iz šeme američke vlade. SAD su krale bogatstvo putem emisione dobiti, prodajući dolare za 1/35 trojne unce zlata, kada su vredeli samo 1/200 trojske unce.
Nixonov Šok ulazi u ’tradicionalni’ novac
Da bi kuća od karata mogla da ostane na mestu, predsednik Nixon je 1971. najavio da će američka vlada privremeno da obustavi konvertibilnost dolara u zlato.
Strane vlade više nisu mogle da polažu pravo na zlato svojim papirnim dolarima, a dolar više nije bio “poduprt” zlatom. Nixon je tvrdio da će ovo stabilizovati dolar.
50 godina kasnije, kristalno je jasno da je ovo samo pomoglo dolaru da izgubi vrednost i da ovaj “privremeni” program još uvek traje.
Pre 1971. godine, sve globalne valute bile su vezane za američki dolar putem Bretton Woods-ovog sporazuma. Kada je Nixon promenio američki dolar iz dolara podržanog u zlatu u dolar podržan dugom, ovim je promenio i svaku drugu valutu na Zemlji.
Sam je učinio da se celokupna svetska ekonomija zasniva na dugovima. Valute više nisu predstavljale zlato, već su predstavljale vrednost državnog duga.
Zlatni Standard se nikada nije vratio
Konvertibilnost američkih dolara u zlato – zlatni standard – nikada se nije vratio.
Od 1971. godine, čitav globalni monetarni sistem pokreće se tradicionalnim “fiat” valutama: poverenjem u vladine institucije da održavaju valutni sistem.
Većina valuta podržana je kombinacijom duga njihove vlade i drugih tradicionalnih valuta poput dolara i evra. Papirne valute više nisu podržane zlatom, imovinom koja je više od 5000 godina služila kao težak novac.
Danas vas vlade prisiljavaju da plaćate porez u njihovoj valuti i manipulišu saznanjima oko novca kako bi osigurale da potražnja za njihovom valutom ostane velika.
To im omogućava da neprestano štampaju više valuta, da bi je potrošili na vladine projekte, uzrokujući inflaciju cena koja jede i smanjuje bogatstvo i plate.
Američka vlada sada prodaje državne obveznice (dugove), poznate kao obveznice Trezora SAD, eng. US Treasuries, komercijalnim bankama u zamenu za američke dolare.
Vlada koristi te dolare za finansiranje svog budžetskog deficita. Komercijalne banke prodaju mnoge obveznice Trezora SAD, koje su kupile, američkoj centralnoj banci, Federalnim Rezervama.
Federalne rezerve plaćaju komercijalnim bankama sveže štampanim novcem “pomoću računara i upisivanjem količine na račun”, kako je rekao bivši predsednik Fed-a Ben Bernanke.
Ove komercijalne banke često zarađuju samo kupujući obveznice Trezora SAD od države i prodajući ih centralnoj banci. Kupujte nisko, prodajte visoko.
Centralne banke ovaj proces kupovine državnog duga – odnosno pozajmljivanja novca državi – nazivaju operacijama otvorenog tržišta.
Kada centralna banka odjednom kupi velike iznose duga, oni to nazivaju kvantitativnim ublažavanjem. Centralne banke javno najavljuju kupovinu državnog duga, ali vrlo malo ljudi razume šta to zapravo znači.
Euro, jen i svaka druga valuta koja se danas koristi funkcionišu slično kao američki dolar.
Da li će SAD ikada vratiti svoj nacionalni dug? Neobična stvar u vezi sa državnim dugom SAD-a je ta što vlada poseduje štampariju potrebnu za njegovu otplatu.
Kao rezultat toga, kada vlada duguje novac, oni samo pozajme još više novca da bi otplatile taj dug, povećavajući nacionalni dug.
Ako vam ovo zvuči kao Ponzijeva piramidalna šema, to je zato što ona to i jeste – najveća Ponzijeva šema u istoriji. Kao i svaka Ponzijeva šema, nastaviće se sve dok su ljudi koji kupuju Ponzijevu šemu budu uvereni da će im biti plaćeno nazad.
Ako ljudi i nacije prestanu da se zadužuju i koriste američke dolare jer nemaju poverenja u američku vladu ili vide da cena robe raste (tj. dolar postaje sve manje vredan), potražnja za dolarom će opadati, što će izazvati začaranu spiralu.
Ova spirala često završi u hiperinflaciji, kao što smo videli u novijoj istoriji sa Jugoslavijom, Venecuelom, Argentinom, Zimbabveom i mnogim drugim državama.
Ovo je način kako funkcioniše novac na vašem bankovnom računu. Novac svake nacije na svetu pati od istih problema kao i perle i novčanice u pričama o Njutoniji i Kejnslandu.
Kako banke i vlade kradu tvoj novac?
Tokom vekova, stigli smo do monetarnog sistema u kojem banke i vlade mogu da štampaju novu valutu za finansiranje svojih operacija i svojih prijatelja u zločinu, dok kradu bogatstvo svojih građana.
Šta će se desiti sa svetom kada novac bude mogao da štampa svaki narod na planeti?
- Bogatstvo onih koji su blizu pravljenja nove valute se povećava
- Vlada i politički povlašćena klasa ljudi, imaju pristup novoštampanom novcu pre svih ostalih, pa mogu da ga potroše pre nego što cene porastu. Na ovaj efekat pokazao je ekonomista Richard Cantillon sredinom 1700-ih i poznat je kao Cantillonov Efekat.
- Cena robe raste (poznato kao inflacija)
- Ne raste sve roba istovremeno u ceni. Roba blizu mesta gde se proizvodi nova valuta – finansijski sektor i vlada – prva raste, i odatle uzrokuje efekt talasa na cene.
- Inflacija se često predstavlja kao promena cene potrošačke korpe, poznata kao Indeks Potrošačkih Cena, eng. Consumer Price Index (CPI). Vlada ima alate za manipulisanje ovim brojem kako bi osigurala da se ona čini niskom i stabilnom, kao što je objašnjeno u našem članku o inflaciji.
- Finansijska imovina često primećuje ogromnu inflaciju, ali bankari to ne nazivaju inflacijom – oni kažu da naša ekonomija cveta! Nakon što su američke Federalne rezerve učetvorostručile ponudu američkih dolara u šest godina nakon finansijske krize 2008. godine, banke koje su dobile te nove dolare, kupile su akcije i obveznice, stvarajući ogroman balon u cenama ove imovine.
- Štednja i životni standard stanovništva se smanjuju
- Plate su jedna od poslednjih “cena” u ekonomiji koja se prilagođava, jer se često povećavaju samo jednom godišnje. U međuvremenu, cene dnevnih potrepština te osobe koja zaradjuje platu neprestano rastu kako novi novac kruži ekonomijom.
- Najviše su pogođeni oni koji žive od plate do plate – a to je 70% Amerikanaca.
- Razlike u prihodima između bogatih i siromašnih se povećavaju, kao što se vidi na grafikonu ispod.
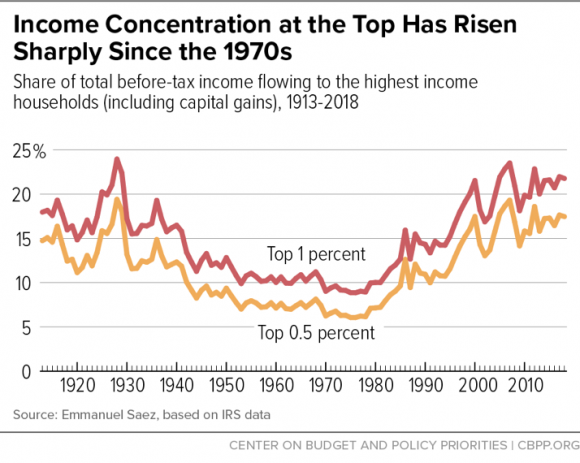 Koncentracija Dohotka na Vrhu Naglo je Porasla od 1970-ih
(Udeo u ukupnom prihodu pre oporezivanja u domaćinstvima sa najvišim dohotkom (uključujući kapitalne dobitke), 1913-2018)
Koncentracija Dohotka na Vrhu Naglo je Porasla od 1970-ih
(Udeo u ukupnom prihodu pre oporezivanja u domaćinstvima sa najvišim dohotkom (uključujući kapitalne dobitke), 1913-2018)Zašto i dalje imamo isti monetarni sistem?
Ako ovaj sistem bogate još više obogaćuje, a siromašne još više osiromašuje, dovodeći do političke nestabilnosti, zašto ga onda ne bismo promenili?
Najveći razlog zašto se ništa ne menja je verovatno to što puno toga ne znamo o samom sistemu. Svi svakodnevno koristimo valute svojih vlada, ali većina nas ne razume kako sistem funkcioniše i šta on čini našim društvima.
Obrazovni sistem, mediji i finansijski stručnjaci neprestano nam govore da je monetarni sistem previše komplikovan da bi ga normalni ljudi razumeli. Mnogi od nas se zato i ne trude da pokušaju.
Još nekoliko razloga zašto ovaj sistem nastavlja da opstaje:
- Mnogo je ljudi koji imaju direktnu korist od štampanja novog novca.
- Ti ljudi ne žele nikakve promene i bore se da zadrže tu moć.
- Nacionalne valute su često pogodne
- Kreditne kartice, online bankarstvo i još mnogo toga čine upravljanje nacionalnim valutama i njihovo trošenje lakim i jednostavnim.
- Građani moraju da plaćaju porez u svojoj nacionalnoj valuti
- To stvara potražnju za tom valutom od svih građana, povećavajući njenu vrednost.
- Glavna međunarodna tržišta, poput nafte, denominirana su u dolarima.
- Nafta je potrebna svakoj zemlji na planeti, ali pošto mnogi ne mogu da je proizvode, moraju da je kupuju na međunarodnim berzama. Od 1970-ih na ovim berzama gotovo sva nafta se prodaje za dolare, što stvara potražnju za dolarima. Da bi se odmaknule od ovog sistema, zemlje bi trebale da pronađu novu valutu ili robu za trgovinu naftom, što zahteva vreme i rizike.
- Nije postojala dobra alternativa
- Uz globalnu ekonomiju u realnom vremenu, naš sistem digitalnog bankarstva koji koristi nacionalne valute je pogodan. Transakcija u tvrdom novcu poput zlata bila bi previše nezgrapna za današnji svet. Digitalna valuta pod nazivom Bitcoin, predstavljena 2009. godine, je rastuća alternativa koja nudi čvrst novac koji se kreće brzinom interneta.
Šta je novac, i zašto trebate da brinete?
Novac je alat koji olakšava razmenu dobara. Kao i svako drugo dobro, novac se pridržava zakona ponude i potražnje – povećanje potražnje povećaće njegovu vrednost, a povećanje ponude smanjiće njegovu vrednost.
Na ovaj način novac se ne razlikuje od kuće ili piletine. Međutim, velika prodajnost novca znači da je potražnja za njim uvek velika. Kao rezultat, novac mora biti težak za proizvodnju (a samim tim i ograničen u ponudi) ili će ga onaj ko ga može napraviti, stvoriti toliko, da vremenom više neće služiti kao zaliha vrednosti. Uskoro će izgubiti svoje funkcije kao sredstvo razmene i obračunske jedinice.
Najbolji novac u datoj ekonomiji je onaj koji se najslobodnije kreće – svi ga žele, lako je obaviti transakcije sa njim i koji sa vremenom dobro drži svoju vrednost. Nijedan novac nije savršen u svemu ovome, a neki ističu jednu funkciju novca na štetu drugih.
Iako se istorija ne ponavlja, ona se rimuje, a usponi i padovi monetarnih sistema imaju jasne ritmove. Uspon i pad monetarnog sistema često sledi opšti obrazac koji smo videli u pričama o agri perlama i Kejnslandu: pojavljuje se odredjenji oblik novca koji pomaže ljudima da efikasnije trguju i štede, ali na kraju gubi na vrednosti kada neko shvati kako da ga jeftino stvori u velikoj količini. Međutim, tokom dugog perioda vremena, monetarni sistemi su se poboljšali u sve tri funkcije novca.
Na primer, zlato je tokom vremena dobro služilo kao zaliha vrednosti. Međutim, naša međusobno povezana ekonomija ne bi mogla efikasno da funkcioniše ako bi trebalo da fizičko zlato zamenimo robom i uslugama. Mnogo je lakše kretati se na papirnom i digitalnom novcu, ali istorija nam govori da su vlade i bankari iskoristili ove oblike novca za krađu bogatstva putem inflacije.
Današnji globalni monetarni sistem je vrlo zgodan, a digitalna plaćanja i kreditne kartice olakšavaju trošenje novca. Ovo skriva stalnu inflaciju koja nagriza vrednost svake jedinice novca i dovodi do sve većeg jaza u bogatstvu.
Nadam se da je ovaj članak proširio vaše razumevanje novca i njegove uloge u društvu. Ovo je samo početak svega što treba istražiti o novcu: za kasnije su sačuvane teme o inflaciji, kamatnim stopama, pozajmljivanju, poslovnim ciklusima i još mnogo toga.
Efikasnija Ušteda Novca
Možda se pitate kako zaštititi svoju štednju kada svaki oblik često korišćenog novca i investicija pati od inflacije ponude – koja umanjuje vrednost i prenosi bogatstvo onima koji mogu da stvore novac ili investiciju. Možda se čini da se ništa na planeti danas ne može kvalifikovati kao ‘težak’ novac, ali dve stvari ipak ostaju: zlato i njegov noviji rođak Bitcoin. Obe ove stvari je neverovatno teško proizvesti, a jedna od njih se kreće brzinom interneta i može se čuvati u vašem mozgu.
Ako želite da saznate više o Bitcoin-u kao sredstvu za zaštitu vaše ušteđevine, pročitajte ovde. Ako ste već spremni za kupovinu Bitcoin-a, pogledajte moj vodič za kupovinu Bitcoin-a. Možete početi sa investiranjem sa samo 5 ili 10 €.

Zasluge
Hvala svima koji su pomogli u izradi i uređivanju ove serije o novcu: @ck_SNARKS, @CryptoRothbard, Neil Woodfine, Emil Sandstedt, Taylor Pearson, Parker Lewis, Jason Choi, mojoj porodici i mnogim drugima.
Hvala svima koji su ovo inspirisali i razvili ključne ideje koje su ovde primenjene: Friedrich Hayek, Carl Menger, Ludwig Von Mises, Murray Rothbard, Saifedean Ammous, Dan Held, Pierre Rochard, Stephan Livera, Michael Goldstein, i mnogi drugi.
Molim vas da šerujete! Ako vam je ovaj članak otvorio oči o tome kako funkcioniše naš novac i finansijski sistem, kontaktirajte me ili ostavite komentar!
Ako vam se sviđa moj rad, molim vas da ga podelite sa svojim prijateljima i porodicom. Cilj mi je da svima pružim pogled u ekonomiju i na to kako ona utiče na njihov život.
-
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ b99efe77:f3de3616
2025-05-12 21:38:36
@ b99efe77:f3de3616
2025-05-12 21:38:36🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
;start () -> greenLight1 redLight2
;toRed1 greenLight1 -> queue redLight1
;toGreen2 redLight2 queue -> greenLight2
;toGreen1 queue redLight1 -> greenLight1
;toRed2 greenLight2 -> redLight2 queue
;stop redLight1 queue redLight2 -> ()Places & Transitions
- Places:
- greenLight1: Indicates that the first traffic light is green.
- greenLight2: Indicates that the second traffic light is green.
- redLight1: Indicates that the first traffic light is red.
- redLight2: Indicates that the second traffic light is red.
-
queue: Acts as a synchronization mechanism ensuring controlled alternation between the two traffic lights.
-
Transitions:
- start: Initializes the system by placing tokens in greenLight1 and redLight2.
- toRed1: Moves a token from greenLight1 to redLight1, while placing a token in queue.
- toGreen2: Moves a token from redLight2 to greenLight2, requiring queue.
- toGreen1: Moves a token from queue and redLight1 to greenLight1.
- toRed2: Moves a token from greenLight2 to redLight2, placing a token back into queue.
- stop: Terminates the system by removing tokens from redLight1, queue, and redLight2, representing the system's end state.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> ()
-
 @ b99efe77:f3de3616
2025-05-12 21:19:53
@ b99efe77:f3de3616
2025-05-12 21:19:53🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
;start () -> greenLight1 redLight2
;toRed1 greenLight1 -> queue redLight1
;toGreen2 redLight2 queue -> greenLight2
;toGreen1 queue redLight1 -> greenLight1
;toRed2 greenLight2 -> redLight2 queue
;stop redLight1 queue redLight2 -> ()Places & Transitions
- Places:
- greenLight1: Indicates that the first traffic light is green.
- greenLight2: Indicates that the second traffic light is green.
- redLight1: Indicates that the first traffic light is red.
- redLight2: Indicates that the second traffic light is red.
-
queue: Acts as a synchronization mechanism ensuring controlled alternation between the two traffic lights.
-
Transitions:
- start: Initializes the system by placing tokens in greenLight1 and redLight2.
- toRed1: Moves a token from greenLight1 to redLight1, while placing a token in queue.
- toGreen2: Moves a token from redLight2 to greenLight2, requiring queue.
- toGreen1: Moves a token from queue and redLight1 to greenLight1.
- toRed2: Moves a token from greenLight2 to redLight2, placing a token back into queue.
- stop: Terminates the system by removing tokens from redLight1, queue, and redLight2, representing the system's end state.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> ()
-
 @ b99efe77:f3de3616
2025-05-12 21:19:41
@ b99efe77:f3de3616
2025-05-12 21:19:41🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
;start () -> greenLight1 redLight2
;toRed1 greenLight1 -> queue redLight1
;toGreen2 redLight2 queue -> greenLight2
;toGreen1 queue redLight1 -> greenLight1
;toRed2 greenLight2 -> redLight2 queue
;stop redLight1 queue redLight2 -> ()Places & Transitions
- Places:
- greenLight1: Indicates that the first traffic light is green.
- greenLight2: Indicates that the second traffic light is green.
- redLight1: Indicates that the first traffic light is red.
- redLight2: Indicates that the second traffic light is red.
-
queue: Acts as a synchronization mechanism ensuring controlled alternation between the two traffic lights.
-
Transitions:
- start: Initializes the system by placing tokens in greenLight1 and redLight2.
- toRed1: Moves a token from greenLight1 to redLight1, while placing a token in queue.
- toGreen2: Moves a token from redLight2 to greenLight2, requiring queue.
- toGreen1: Moves a token from queue and redLight1 to greenLight1.
- toRed2: Moves a token from greenLight2 to redLight2, placing a token back into queue.
- stop: Terminates the system by removing tokens from redLight1, queue, and redLight2, representing the system's end state.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> ()
-
 @ eac63075:b4988b48
2024-10-21 08:11:11
@ eac63075:b4988b48
2024-10-21 08:11:11Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.

Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.

The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.

Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.

The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.
 Table reference: Patrick Breyer - Chat Control in 23 September 2024
Table reference: Patrick Breyer - Chat Control in 23 September 2024Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.

The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.

User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.

The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.

Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ fbf0e434:e1be6a39
2025-05-13 02:00:02
@ fbf0e434:e1be6a39
2025-05-13 02:00:022025年3月17日
塔林·克里斯滕森(Taryn Christiansen),DoraHacks
特别感谢DoraHacks创始人Eric Zhang提供的深刻讨论和支持。
Part 1
自动化的浪潮无疑正在到来。人类劳动将迅速贬值。人工智能已经取得了巨大的进展,并且,随着许多创新降低了成本,越来越多的企业将能够整合这一技术。随着生产模式、资本和供应链越来越多地实现自动化,生产力和效率将加速发展。
问题是,这是否是好事。答案五花八门。从末世论者如埃利泽·尤德科夫斯基(Eliezer Yudkowsky)[1]和罗曼·扬波尔斯基(Roman Yampolskiy)[2]等人认为,人工智能有潜力——并最终将——消灭人类物种。人类将远远不如未来的人工智能高效,因此,当通用人工智能(AGI)得以实现时,智能机器很容易得出结论:人类消耗太多,世界没有人类会更好。然后是怀疑论者,如马克斯·泰格马克(Max Tegmark)[3],他认为应该暂停人工智能的发展,以便更好地将其与人类利益对齐。“只有当我们确信其影响将是积极的、其风险可控时,才应开发强大的人工智能系统。[4]”再者,也有技术乐观主义者,如马克·安德森(Mark Andreessen)[5]、萨姆·奥特曼(Sam Altman)[6]和雷·库兹韦尔(Ray Kurzweil)[7],他们主张人工智能将带来物质上的丰盈乌托邦。发展应该加速,监管者应当退让,未来将带来经济增长、生产力提高和生活水平的惊人提升。
[1] 美国人工智能理论家、作家,MIRI(Machine Intelligence Research Institute,机器智能研究所)创始人之一。 [2] 俄罗斯裔美国计算机科学家,路易斯维尔大学教授,专长于AI安全和人工智能伦理。 [3] 瑞典裔美国物理学家、MIT教授,Future of Life Institute(未来生命研究院)联合创办人。 [4] https://futureoflife.org/open-letter/pause-giant-ai-experiments/. [5] https://a16z.com/the-techno-optimist-manifesto/. 硅谷知名风险投资家、网景(Netscape)浏览器联合创始人,Andreessen Horowitz投资公司创始人。 [6] https://ia.samaltman.com/. OpenAI CEO. [7] 发明家、未来学家、作家,现为谷歌工程总监。
在这里很难做出具体的预测。不同立场的人常常以某种“不可避免性”的口气宣扬他们的观点。安德森是乐观主义最著名的主张者之一,他坚信由快速技术进步所带来的未来将是每一代人梦寐以求的那种未来。将会有具备无限同情心和耐心的人工智能导师,使教育更加普及和易获取;医疗行业将大幅提升,提供更好的预测并减少错误;机器人可以执行危险的工作,从而让人们追求自己的愿望。经济效益也将是巨大的。由于生产成本的降低,价格将更低,人们的钱将有更强的购买力,需求将增加,新的工作岗位将被创造,工资也将提高。他主张这一观点的主要论据是历史先例。每次有新技术革命到来时,社会总会从中获得净效益(net good)。十九世纪石油工业的形成之前,鲸鱼行业雇用了成千上万的工人。石油取代了这些工作,但也消除了依赖屠杀成千上万头鲸鱼来制造日常产品的需求。汽车威胁了许多行业,但当它成为普遍拥有的财产时,突然之间,需要更多的道路、桥梁和加油站来满足需求。虽然将会有自动化,人工智能将以良好的成果充斥世界,赋予经济前所未有的机会,让人们找到工作、积累财富,并利用人工智能所创造的价值。
然而,人工智能不同于以往的技术发展。人工智能是一种智能的进步和普及,而不仅仅是机械化的进步。库兹韦尔写道:“第一次工业革命扩展了我们身体的能力,第二次则扩展了我们思想的能力。”但是,一种新变量意味着结果的不同。人工智能能够学习、适应、生成、发现、反驳、怀疑、确认、设定目标,能够制定手段,也许有一天它会拥有意志并感知情感。它变得越来越具能动性(agentic)和自主性(autonomous),能够承担和完成通过它自身流程所生成的任务。如果它现在还没有具备能动性,那目标是让它达到这一点。仅仅基于先前经验得出的预测可能是一种范畴错误,容易导致误导和错误。当然,过去的技术形式与人工智能之间存在重叠,但它们之间有一个明确的区别,并且这种区别应该指导我们的预测。
另一方面,末世论者的观点并不具备很大的现实意义。那些通常潜藏在末世论者警告背后的“终结者”般的情景是不太可能发生的。尽管正如埃隆·马斯克(Elon Musk)[8]最近在《乔·罗根播客》(The Joe Rogan Podcast)上所言,如果嵌入了错误的目标,也许像“太空奥德赛(Space Odyssey)”系列作品中的HAL 9000那样的情景[9]是可能的。考虑到DeepSeek公司最近在降低计算成本方面的进展,该公司开发的AI模型已具有与美国最先进的模型竞争的水平,一场新的竞赛已经宣告开始,事情将会加速发展。美国副总统在人工智能行动峰会上的讲话清楚地表明了这一点。当前存在着一场争夺国际技术主导地位的竞争,这将塑造未来,发展速度的减缓等同于举白旗。因此,如果对安德森的主张有任何可行的反对意见,那也必须集中在如何引导技术发展,而非停止它。这应当为关于自动化的讨论提供启示:如何最好地引导自动化以避免不良结果?我们需要一种积极主动的方式。
[8] 特斯公司CEO,SpaceX创始人兼首席执行官,X(原Twitter)所有人。 [9] HAL 9000(简称HAL)是科幻小说和电影系列《太空奥德赛》中的虚构人工智能角色,由阿瑟·克拉克(Arthur C. Clarke)和斯坦利·库布里克(Stanley Kubrick)共同创作。在作品中,HAL 9000原本是飞船“发现号”(Discovery One)的中央控制系统,它被设计得极其可靠,拥有高度智能、情感模拟能力,负责飞船运行,包括导航、生命支持、通信等核心任务。在执行任务时,由于HAL开始表现出微妙的异常(如错误报告设备损坏),同行宇航员决定关闭HAL。当这一计划被HAL得知,HAL控制飞船上设备造成了同行宇航员的死亡。但后续作品揭示,HAL的表现是由于收到了相互冲突的人类指令,并决定杀死宇航员来保证两种指令都能够实现。
Section 1.1
安德森对自动化的乐观态度存在一个问题,那就是他过于确定新工作机会会得到足够的分配,供人们享受并加以利用。问题在于,经济正变得越来越依赖知识和信息。知识和信息的比重远远超过了体力劳动,而在市场上能够取得成功的人是那些拥有相关技能的人,这些技能需要通过教育和培训来获得。正如托马斯·皮凯蒂(Thomas Piketty)[10]在其《21世纪资本论》(Capital in the Twenty-First Century)一书中所观察到的,这是一个普遍的经济趋势,“趋同(即减少和限制不平等)的主要动力是知识的传播和对培训与技能的投资。”因此,随着经济日益依赖知识,那些没有相关技能或安全保障的失业工人将处于严重的不利地位。而那些拥有相关知识、技能和信息的人则更有优势,能够投资资本并增加财富。例如,即便经济增长和生产成本降低,那些没有技能的人将看到工资停滞不前。但是,假设由于生产成本降低,消费者的购买力增强,需求可能会上升,如果供应无法迅速满足这一需求,价格可能会随之上涨,从而引发需求拉动型通货膨胀。关键在于,经济和生产力增长可能无法自然应对的变量和情境。正如皮凯蒂所说,“没有自然、自发的过程能够防止不稳定、不平等的力量永久占据主导地位。”因此,必须采取积极的应对策略,来避开那些可能会导致漂浮在经济表面上的大量船只沉没的尖锐岩石。
[10] 法国经济学家。
在杰里米·里夫金(Jeremy Rifkin)[11]的《工作的终结》(The End of Work)一书中,他采用了更加严峻的语气:“(下一个)工业革命正迫使全球经济面临空前的危机,数百万人因技术创新失业,全球购买力急剧下降。”而埃里克·布林约尔松(Erik Brynjolfsson)[12]和安德鲁·麦卡菲(Andre McAfee)[13]在《第二次机器时代》(The Second Machine Age)[14]一书中提供了充分的理由,认为里夫金的观点具有一定的道理。他们认为,经济增长所带来的回报(bounty)——即通过较少的投入产生更多的产出,使商品更加便宜、更加易得,从而改善人们生活——并没有通过财富、收入和资本的分配,使每个人都被惠及而受益。换句话说,“科技进步的浪潮可能并不会使所有船只都得以提升。”例如,在上文提到的技能差距上,“自1970年代中期以来,拥有研究生学位的人的工资上涨了约25%,而高中辍学者的平均工资则下降了30%。”尽管自20世纪中期以来,美国GDP和经济生产力呈现“令人印象深刻的轨迹”,但该国的中位数收入却在下降,表明少数人正在获得好处,而大多数人却错失了机会:自里根时代以来,贫富差距不断扩大。布鲁金斯学会的这篇文章[15]也支持这一观点。
[11] 美国经济和社会理论家、作家、公众演说家、政治顾问和活动家。 [12] 经济学家、教授,现任斯坦福大学数字经济实验室主任。 [13] 研究员、作家,MIT斯隆管理学院副教授、MIT数字经济计划副主任。 [14] http://digamo.free.fr/brynmacafee2.pdf/ [15] https://www.brookings.edu/articles/rising-inequality-a-major-issue-of-our-time/
然而,也许这些观点的实际含义被错误的同情心所误导。尽管不平等的确存在,但这并不意味着它应该被视为最主要的关注变量。再次强调,技术创新使商品变得异常便宜,使人们的生活更加轻松、生活水平更高,并且通过提供更多商品、服务、信息和知识的可获取性,来满足人们的需求和愿望,从而让日常生活更便利。尽管财富分配可能存在不平等,但其整体增长使每个人都变得更好。而且,随着财富的进一步增长,这一趋势将持续。曾经只有富人能够负担得起的东西,如今大多数人都可以买得起。比如iPhone,它能提供比所有现存图书馆更多的信息,而历史上,只有最富有的人才能使用后者,而几乎任何人都能购买前者。欧洲最大的图书馆是1481年的梵蒂冈图书馆,馆内估计有三千五百本书籍和文献。ChatGPT估计,如果将网上的信息转化为书籍大小的量,将约合467千万亿本书。看看农业的发展。当经济学家米尔顿·弗里德曼(Milton Friedman)在1980年写《选择的自由》(Free to Choose)时,他写道,在《独立宣言》被签署的时代,“每20个工人中就需要有19个(从事农业劳动),以养活这个国家的居民,以及提供生产盈余以供出口,来交换外国商品。如今,只需要每20个工人中的不到1个工人,就能养活2.2亿美国居民,并提供生产盈余使美国成为世界上最大的食品出口国。”
彼得·蒂尔(Peter Theil)[16]常常宣称,问题是技术创新停滞,而不是与福利项目或分配模式相关的道德失败。科学和技术需要突破,以转变行业并提高生活标准。人工智能的智能革命,理应能够实现这一潜力。因此,也许最好是直接放手不管。专注于特定分配模式的公平或正义,就像尼采所说的那样,是一种“坏良心(bad-conscience)”——以被认为的集体利益为代价而追求个人利益时所体验到的罪疚感,但实际上,这种感受只会阻碍进步,而非推动它。真正和最好的目标,可以说是努力创新并创造推动历史发展的价值,这就像亚当·斯密(Adam Smith)[17]的“看不见的手”的隐喻一样,自然地调和了人们的自利。正如米尔顿·弗里德曼所说,“对于促使个人之间合作,进而使得每个个人都可以从合作中受益的状态而言,没有外部力量是必要的,没有对自由的侵犯是必要的。这就是为什么正如亚当·斯密所说的,‘只关心自身利益’的个人会‘被一只隐形之手引导,以推动一种与他的意图无关的目标’。”
[16] 硅谷投资人,PayPal创始人,企业家、风险投资家、政治思想家、作家。 [17] 经济学家、哲学家、道德理论家,古典经济学奠基人。
Section 1.2
关于经济增长是否足以改善长期的福祉和生活水平的问题,存在着高度争议。这个问题显然在这里无法解决。然而,提到这一点的目的是为了表明两种观点都具有正确性。个人在市场上追求自己的利益,像价格和工资这样的变量通过人们的自愿交换达成平衡,已经带来了巨大的成果。但差距也随之产生。
自动化是一个潜在的威胁。忽视它并声称它是危言耸听是一个错误。在可能的人工智能颠覆之后,某种形式的平衡达成之前,过渡期可能是复杂的,并且可能造成不必要的痛苦,如果事先处理,这些痛苦本可以避免。革命性的新技术可能既有好的一面,也有坏的一面。例如,十五世纪的印刷术使人们摆脱了教会强加的信息控制,催生了科学文献涌现的浪潮,为文明提供了巨大的价值。但它也导致了激烈而血腥的宗教战争,因为它允许人们传播各种信息。因此,为了避免类似的结果,在实施任何能够重新安排和重组社会经济安排的技术时,采取主动的方式非常重要。
从这里出发,通常的推论是,监管措施是应对这些可能性最好的手段。但与其满足于监管,正如马克·安德森在拜登政府执政期间警告的那样,监管会导致人工智能垄断,本文将力图支持自由市场中的自愿交换,同时促进必要的社会合作,帮助人们适应并在一个越来越不依赖于人力资本的经济中发挥作用。
本文的担忧是人们失去行使自身能动性(agency)的机会,从而无法拥有对自己的生活的控制(control)感和影响(influence)感。如果大量的人失去参与工作的机会,将会出现一条鸿沟,阻挡人们在世界中通常实现自己潜力的方式。他们将不再有机会在关键的社会领域做出具有深远影响的生活选择,这些选择需要谨慎和远见。人们将失去测试自我、发现天性的倾向和兴趣、辨认自己重视的事物以及行使选择去追求它的机会。社会中培养毅力、动机和个人意志的主要机会将会丧失。如果工作将主要被自动化替代,那么需要一个新的机会媒介来取而代之。作为社会制度的工作需要进步,并保持人们成长和发展的途径。
20世纪的自由主义哲学家约翰·杜威(John Dewey)写道:“正如感觉需要可感知的对象来刺激它们,我们的观察、回忆和想象能力也不是自发工作的,而是由当前社会活动所设定的需求激发。”像教育和工作这样的社会环境提供了刺激特定能力和功能所需的活动媒介,这些能力和功能需要完成定义活动的任务。人们常常争论说,自动化将使人们摆脱繁琐和机械的工作束缚。他们将有更多时间寻找新的方式来表达自己的需求,并最终实现工作一直阻碍他们实现的目标。人们将有自由去实现自己的潜力。但这一切不会自发发生。需要有能激发实现真正自由、意义和目的的活动的环境。当一个人完全孤单地待在一个没有人阻碍其动作和倾向的房间里时,可以说他是自由的。这样的人可以随心所欲。但由于没有能够激发适当反应的情境,且没有成功与失败的可能性,也缺少需要合作和协调的场景,这些场景有助于培养社会和情感的能力,也没有必要发挥智力和解决问题的能力,这个房间里的人的成长会停止,反而会枯萎,无法实现自由。一个从天空自由下落、不被任何东西阻挡的人,他看似自由,其实并不自由,因为他注定会撞向地面。
正如弗朗茨·卡夫卡(Franz Kafka)所写:“我自由了,因此我迷失。”哲学家让-保罗·萨特(Jean-Paul Sartre)则说:“人类被注定要自由。”
因此,当前的问题是,如何开辟一个人们能够自愿进入其中,并找到表达美好生活所需能力的机会的空间。此类机会,旨在行使人们的能动性,将被称为“质性丰富(qualitatively rich)机会”,而能够实现这些机会的环境则被称为“质性丰富环境”。
一个体现“质性丰富机会”的“质性丰富环境”是“开源生态系统”(open source ecosystems),它应当是人工智能发展的主要模式,它提供了以下框架:市场将为人们提供机会,让他们通过具有挑战性和刺激性的工作来行使自己的能动性,进而实现有意义的项目。人们将不得不学习新技能,克服障碍,但这一过程不仅是为了保持一个人们可以竞争、做出选择、发展能动性的市场,同时也促进人们生活中的目的和意义。如果经济要关上旧有工作形式的门,比如流水线和服务性工作,那么应该为人们提供更多有意义的工作机会。正如经济学家泰勒·科文(Tyler Cowen)在《莱克斯·弗莱德曼博客》(Lex Fridman podcast)中指出的那样,人们需要事情做。他们不想只是待在家里,正如COVID封锁所证明的那样。如果例行劳动和低技术劳动将被自动化,那么唯一的选择是确保存在“质性丰富机会”,以便人们能够利用并行使自己的能力,进行有意义的工作。
因此,应该在经济中引入一种新的范式。从佩卡·希曼宁(Pekka Himanen)[18]的《黑客伦理》(The Hacker Ethic)一书中汲取灵感,人们应当从以工业为基础的工作范式转向一种“黑客范式”。在工业范式中,个体主要执行重复性的劳动任务,其目的仅仅是为了获取收入以维持生存。而黑客范式则以内在价值为核心,强调工作本身的趣味性、刺激性、创造性与游戏性,其特征是激情与游戏,而非“履行对工作的责任”或“为经济做出贡献”的社会义务,正如马克斯·韦伯(Max Weber)[18]在《新教伦理与资本主义精神》(Capitalism and The Protestant Ethic)中所揭示的那样。黑客范式强调人类能动性及其实现价值的潜力,这种价值能提升人类。工业范式则在工人与他们与世界的积极参与之间产生疏离感:工人对他们所贡献的工作漠不关心;人们通常不喜欢甚至讨厌他们的工作。他们在那里是为了赚钱,而不是参与有意义的工作。正如希曼宁所写:“改革工作形式不仅是尊重工人的问题,更是尊重人类作为人类的问题。黑客不认同‘时间就是金钱’的格言,而认同‘这是我的生活’的格言。”正如埃里克·史蒂文·雷蒙德(Eric Steven Raymond)在《如何成为黑客》(How To Become A Hacker)[20]中所说,黑客认为世界充满了奇妙的问题,并在致力于解决这些问题中找到了自由。他们寻找需要动机和热情的项目,并相信当其他人也有机会获得同样的自由时,世界将变得无限美好,这需要社会合作以及对信息的最大程度的开放获取——这也正是“开源”的重要意义所在。
[18] 芬兰哲学家。 [19] 社会学家、经济学家、历史学家、政治学理论家,德国社会学与历史学传统的代表人物之一,被称为现代社会学的奠基人之一。 [20] http://www.catb.org/esr/faqs/hacker-howto.html
为了凸显为何引入新范式对于应对人工智能的挑战至关重要,具有显著的历史意义,我们可以回到亚当·斯密的思想。随后,将进一步阐明“质性丰富环境”与“质性丰富机会”的概念,并将其应用于当下以专有技术(proprietary technology)为核心的人工智能垄断体系。届时可以看到,这些垄断将扼杀黑客范式的生成,因此是不可取的。
透过亚当·斯密的视角我们可以看到,尽管工业化在长期内极大地提升了人们的生活水平,但它也对从事重复性、机械性劳动的人产生了消极影响,因为这类劳动削弱了对人类认知能力的刺激,阻碍了其全面发展。劳动分工极大地加速了专业化的进程,却减少了个体接触那些能调动其高级心智能力的机会——而这些能力正是实现有意义、有目标、富有成就感的工作的基础。人工智能与自动化正成为一种转型催化剂,逐步替代工业时代的工作模式与生产逻辑,将人力资本曾承担的任务转交予智能机器完成。若人工智能真的是一种进步——即人类进步——那么它就应回应亚当·斯密关于劳动分工及其对人类生活影响的担忧。
Part 2
Section 2.1
亚当·斯密在1776年写下了《国富论》(The Wealth of Nations)。受到艾萨克·牛顿(Isaac Newton)的影响,斯密希望理解社会背后的设计,以及社会的运作机制,类似于牛顿发现并使用采用机械论术语来公式化了解释宇宙的物理法则。那个时代的模型是将现象看作是像精密调校的手表一样有组织和有秩序的,所有部件和机械都在完美的和谐中协同工作,产生各种各样的效应和涌现现象。
在斯密生活的时代,第一次工业革命正在英格兰进行。城市扩张,曾经仅限于富人阶层的商品和服务变得更加廉价且易于获取,生活水平提高,基础设施得到了发展,表面上看,人们过上了前所未有的更好生活。斯密观察到社会的进步。由于大发现时代以及使欧洲人能够踏上新大陆的技术,欧洲人与那些似乎尚未经历欧洲所经历的历史进程、被欧洲人认为是“未开化”的民族接触,因此,欧洲大陆的风尚(ethos)是历史和文明正在进入一个新的、更为先进的阶段。科学探索和知识带来的创新提升了生产力和效率,从而使社会系统的组织更加复杂。斯密希望了解推动这一进程的因果机制。
斯密观察并认为劳动分工在社会经济中扮演了主要的,甚至是基础性的角色。随着社会组织的扩展,制造与生产过程逐渐细分为更为专业的任务,结果这些过程的产出大幅增加。在传统的行会框架中,工匠将一生投入到完整的手工业中,学习所需的所有方面并精通每一部分。这种行会框架逐渐被分工化的工厂模式所取代,后者在日益发展的城市中通过劳动分工的方式系统化生产。一个庞大的个体系统因此浮现,它需要极高的协调性,而劳动分工则将这一系统组织成一个复杂的机制,旨在调和人们的利益。
斯密还认为,劳动分工反映了人类本性中的某些更深层次的特征。人们涌向城市,赚取劳动报酬并享受更好的生活条件,因为斯密认为,人类天生具有进行交换(truck)、易货交易(barter)和贸易(exchange)[21]的倾向。他写道:“交换、易货和将一种物品与另一种物品贸易的倾向是所有人类共有的,在其他任何动物种群中都无法找到。”像狼这样的动物自然地在等级化的群体中组织自己,刚孵化的小鸟倾向于飞行,而像树木这样的有机体则在密林中争夺阳光。与此不同,人类进行交换、易货和贸易,是因为他们有天生的倾向来改善自身状况。劳动分工推动了这一目标的实现。
[21] 这三个词的区别在斯密研究中并没有得到广泛讨论。一些学者认为它们是同义的,通过重复表达强调(参考J.Z. Muller, (1993) Adam Smith in His Time and Ours: Designing the Decent Society, New York: Free Press第69页,Willie Henderson and Warren J. Samuels, (2004) The etiology of Adam Smith’s division of labor, in Essays on the History of Economics)。就这三个词在英语中的使用历史而言,truck system在英国曾经意为用实物作为工资的薪资制度,barter通常指不涉及货币的物物交换。
然而,斯密认为,劳动分工是一种权衡——它也有代价。尽管人们的生活水平提高,他们享受更好的条件,能够满足诸如食物、水和住所等消费需求,但劳动分工却将工人简化为机器中的齿轮。这些任务几乎不需要认知努力。一旦任务变得常规化,并转化为肌肉记忆后,便没有更多的障碍或问题需要克服。因此,斯密深切担忧这一过程将随着时间推移产生深远的负面认知效应。人们去上班,只要他们熟悉自己的任务,就不需要动脑;他们机械地行动。斯密直言不讳地写道:
“一个人一生都在执行少量简单的操作,并且这些操作的效果始终显而易见,他便无需发挥理解力,或利用自己的创造力去寻求解决从未出现的困难的方法。他自然会变得愚笨无知,几乎达到人类可能变得最愚笨和无知的地步。”
劳动分工提供的机会在质性上较为贫乏,无法使人们具备过上有意义和有目的生活的能力。借用另一位启蒙时期哲学家伊曼纽尔·康德(Immanuel Kant)的术语,劳动分工未能尊重人类的尊严,而尊严要求针对并培养那些能够使人过上自主选择生活所必需的能力。拥有尊严意味着对个人生活拥有影响力(influence)和掌控力(efficacy)。
劳动分工创造了更多提高生活水平的机会,但它没有提供“质性丰富机会”,使人们能够整合他们的能力并实现全面的人生。大多数人可用的机会并未促使他们将创造性和生产力能力集中于那些能够扩展他们在世界中自由感的目标上。与行会制度相比,劳动分工提供了更多的机会,但这些机会也更浅薄,更缺乏产生掌控感的体验。但由于生活水平较高,人们正确地选择了将自己降级为齿轮的工作。但正如斯密所观察到的,提高生活水平不足以满足人类需求的全面范围。它没有让大多数个体能够发挥他们的更高能力。
斯密认为,必须进行改善。对人们而言,更多“质性丰富机会”是至关重要的,这些机会使他们能够过上更有意义和目的的生活,体现人类尊严,并为行使他们的能动性提供基础。劳动分工提供了物质自由的增益,但并未提供足够的机会以实现更内在的、主体驱动的自由。
这无疑是卡尔·马克思对资本主义的重大批评之一。在资本主义体制下,人们与他们的劳动发生异化(alienation)。劳动的异化意味着人们与自己的活动脱离;即人在其自身和它的创造与生产能力之间产生了距离。在心理学家埃里克·弗洛姆(Eric Fromm)关于马克思的著作[22]中,他写道:“对马克思而言,异化的过程表现在工作和劳动分工中。工作是人类与自然之间的积极联系,是创造新世界的过程,包括创造人类自身……但随着私有制和劳动分工的发展,劳动失去了作为人类力量表达的特性;劳动及其产品变成了与人类、与他的意志和计划分离的存在。”
[22] Eric Fromm, Marx's Concept of Man.
人类通过他们所参与的活动以及在其中投入的内在力量和驱动力来理解和塑造自己的身份。通过创造和塑造世界及其环境,并将能量集中于外部项目和目标,一个人在世界中实现自我感。活动(Activity),而非被动的消费或任务,定义了马克思所说的人类本质。正如弗洛姆在其著作《拥有与存在》(To Have or To Be)中所指出的,通过“存在(being)”,而非“拥有(having)”,一个人才能体验到生活的意义和目的。通过“在爱中存在”,“以充满激情的方式存在”,“以积极行动的方式存在”,“以有希望的方式存在”,“有目的地存在”,以及“以有生产力地方式存在”,一个人才能过上充实的生活,而不必依赖“拥有”(爱、激情、积极性,等等)这些东西。劳动分工强调“拥有”,而其所涉及的许多工作和活动并未促使人们发展出“存在感”。正如德国诗人歌德(Johann Wolfgang von Goethe)所言,人类通过“将自己从可能性的黑夜转化为现实的白昼”来努力存在。人类通过外化他们内心的价值观和设想来追求成为自我,而这一过程通过活动得以实现。弗洛姆写道:“人类只有在生产性行为中才是活着的,只有在他通过表达自己特定的人类能力来把握外部世界,并且以这些能力来把握世界时……在这个生产性过程中,人类实现了自己的本质。”劳动分工减少了人类的能动性感,即人类以他们所珍视的、选择并在其上实践自身意志的有意义的方式,来主动影响和引导自己生活的能力。
通过创建“质性丰富环境”,黑客范式及其对开源的推动提供了多个“质性丰富机会”,从而推动了我们社会和政治结构的进步。它具有实现人类天性中更为积极的一面——人的能动感——的潜力,而不仅仅是其消极和消费的部分。这里的主要假设是,如果人工智能要发展并融入经济基础,它应当使人们的生活得到改善。更具体地说,如果自动化发生,其结果应当是改善人们的生活,而非对他们造成伤害。实现这一目标的一种途径是确保足够分配“质性丰富机会”,让每个人都能从中受益,而开源正是实现这一目标的途径。人工智能发展可能导致人们境况恶化以及抑制他们潜在机会的一个重要原因是存在使用专有模型来控制人工智能并主导其市场使用的垄断现象。黑客范式和开源则为避免这种结果提供了可能的解决方案。
Section 2.2
在理解垄断如何减少“质性丰富机会”之前,我们需要进一步弄清楚什么是“质性丰富机会”,以及它们激发并帮助发展哪些能力。在解释这类机会的性质及其意义之后,我们将探讨垄断是如何大幅削弱这些机会的可及性,以及这意味着什么。
“质性丰富机会”的理念源自亚里士多德(Aristotle)[23],更具体地说,是由哲学家玛莎·努斯鲍姆(Martha Nussbaum)和经济学家阿玛蒂亚·森(Amartya Sen)进一步发展的。亚里士多德认为,人类要实现繁荣、过上充实而有尊严的生活,必须达成某些特定的功能(functions)或方式。他认为存在一种“人性(human nature)”,而这种人性包含基本的和更高层次的需求。无论历史和偶然条件如何变化,人类都具有一些根本特征。当然,这些特征是在历史情境中体现的,但在所有文化和文明中都可以观察到某些本质上的一致性。亚里士多德说:“善是万物所追求的目标。”所谓“善”,即是一种事物的适当功能。例如,眼睛的善是“看见”,种子的善是“长成一棵树”。实现某物的适当功能,就是实现其“繁荣”(flourish),也就是达到它所追求和努力趋向的状态。达到这样的状态,就是获得一种内在价值。
[23] 古希腊哲学家。
作为一个人去实现其功能,需要基本的生活必需品,如食物、水、住所和行动能力。但这些物品本身并不具有内在价值;它们之所以有价值,是因为它们使人能够运作以追求更进一步、更有内在价值的事物。如果一个人仅仅拥有这些基本的生存条件,我们可以说他“运作”着,但未必是“良好地运作”。要使一个人“良好地运作”,必须拥有其他内在价值更高的资源。人类需要教育与信息获取,以发展其认知能力;需要家庭和亲密关系,以发展社交技巧、个人身份认同和情感处理能力;还需要能够施展意志、探索兴趣、投入热情的追求,并培养目标感的渠道。一个良好的政治与社会安排,即我们应当追求的那种社会制度,应当为人们提供具体的机会,让他们得以实践这些需求,从而实现良好的人类运作状态。“质性丰富机会”即是指那些能够为人类发展内在有价值的能力(如做出知情决策的能力、制定值得追求的目标及其实现路径的能力,以及建立有意义、有影响力的人际关系的能力)提供基础的机会。像工作、教育、社区和艺术等社会制度,正是那些激发并促进实现这些目标所需能力的质性丰富环境。
质性丰富机会之所以重要,是因为它们使人们具备发展“能动性”的能力。借用斯坦福大学心理学家阿尔伯特·班杜拉(Albert Bandura)[24]的概念,我们可以将“人类的能动性”理解为个体感受到自己对生活有控制和影响力的能力。更具体地说,质性丰富机会能够激发那些针对“自我效能”(self-efficacy)能力的行为。所谓“自我效能”,是指一个人在面对挑战和障碍时所拥有的自我信心感。当面对一个困难且新颖的任务时,高自我效能的人会评估自己有能力克服困难完成任务;他们会拥有坚持不懈、克服失败的动机;即使身处陌生与复杂情境中,他们也能维持良好的心理状态。质性丰富机会旨在发展那些能够提升自我效能以及应对具体情境所需的能力。通过这些机会,一个人得以锻炼其能动性、获取掌控力,从而扩展其自由感。而正如班杜拉(1994)[25]所说:“一个人自我效能感越强,他为自己设定的目标挑战越高,并且对这些目标的承诺也越坚定。”因此,通过增强自我效能,无论是在信念层面还是实践层面,个人将获得更高程度的自由,并过上更具质感、更丰富的人生。
[24] https://happyheartfamilies.citymax.com/f/Self_Efficacy.pdf [25] https://happyheartfamilies.citymax.com/f/Self_Efficacy.pdf
工作在塑造个体身份和自我认同方面具有至关重要的作用。它为人们提供了探索不同职业路径的机会,使他们能够发现自己在人生中希望追求的目标。工作往往也是建立职业与个人关系、融入不同社会网络的重要方式,同时也是人们获取能力、攀登社会阶梯的媒介。工作这一领域还能帮助人们在多种环境和情境中培养动机、智力以及态度。换句话说,工作为人们提供了发展某些功能或生活方式的机会,而这些功能和生活方式正是实现美好生活所必不可少的。
例如,想象一个年轻人第一次进入劳动力市场。他尝试了几份工作。他发现自己不太喜欢零售业,因为需要持续与顾客打交道。他又尝试了送货服务,结果发现自己不喜欢那种日复一日的重复性工作。最后,他在一个建筑工地找到了工作,并发现有些任务既有趣又具有挑战性。他喜欢动手工作的感觉,于是决定投身技工行业。这个人随后进入技校学习,建立起重要的人际关系,在新环境中受到挑战,被激发去提升技能、积累知识与经验,并在这个过程中不断面对和克服新的困难与障碍。毕业后,他抓住了一个机会——一位欣赏他职业精神的导师为他提供了许多关注和支持。之后,他在某家公司工作了一段时间,并在这个过程中积累了足够的知识和自信,决定创办自己的公司,以实现这个目标。他开始建立客户关系,专注于能让自己在竞争中脱颖而出的技能,并最终打造出一家成功的企业。
这听起来也许有些理想化,但却是一个既熟悉又现实的例子。它描绘了一种有目的的生活,这些目的是通过在环境和情境中发现的机会而形成的,这些环境和情境提供了能够产生能动感和自我价值感的体验。当然,要实现这样的人生画面,通常还需要一系列其他条件,例如成长于一个有支持的环境中,拥有探索个人兴趣所需的资源和时间等——但在美国,工作无疑是提供发展构成美好生活的关键功能的核心渠道。上文中的这个人通过学习新技能、克服挑战、做出关键选择来应对社会环境,最终实现了成功与成就。随着在专业领域的成长,他不断设立新的目标,并获得足够的自我效能感,相信自己能够实现这些目标。他发展出一整套完整的能力体系,最终也获得了尊严感。无论这个人过去或未来是否还拥有其他美好的人生经历,如果没有那些能够让他工作与成长的机会,他的人生质量将会大打折扣。
这里有一个真实的例子,不过这个人将保持匿名。在荷兰大学毕业后,他不想找一份“普通的工作”,于是开始前往其他国家旅行。他靠在 YouTube 上制作音乐赚了一些钱,住在各地的酒店和青年旅舍。但随着资金逐渐减少,孤独与疏离感开始加剧,他变得抑郁。他完全自由——可以去任何地方、看任何东西,做任何他想做的事——但他感到极度孤独。在亚洲的一家青年旅舍,他一个人躺在床上盯着天花板,没有钱、没有女朋友、也没有工作,他想起了父亲曾对他说的话:“他小时候教过我:每当我感到沮丧或者不知道做什么时,就去找一座沙堆,拿把铲子,把沙子从院子的一边搬到另一边……干点体力活,做点辛苦的事——做点什么。我做创业项目时也一样。”于是,他开始学习编程,开发软件和应用程序,并利用 Stripe 平台[26]将作品发布给公众以筹集资金。他专注于那些能够带来方向感与创作机会的活动。在真正的“黑客精神”指引下,他把世界看作充满待解决问题的迷人场域,有些问题他认为是可处理且值得去做的,于是尝试去解决。令人惊讶的是,他立下目标:一年内创办十二个初创公司——而他真的做到了。
[26] 一个专注于在线支付处理和金融基础设施的平台,帮助企业在互联网上管理资金流动。
这个人起初感到疏离与孤独,缺乏人生目标。因此他选择行动起来,把自己投入到使用基础编程语言与工具进行的创造性表达中。通过利用人工智能,他也更能创造出具有价值和实用性的产品,供他人使用与体验。他采纳了父亲的建议,将自己投入到实际行动中,结果是抑郁与焦虑逐渐缓解。他在信息丰富的环境中,发现了许多“质性丰富机会”,得以发展自我,提升自我效能感与能力。他与更多富有挑战性的目标建立联系,不断努力达成这些目标。而开源技术在这一过程中扮演了关键角色。
这也正是 Dora 生态系统的重要意义所在。通过像 DoraHacks.io 这样的平台,像上文所描述的那样的人们可以借由“质性丰富机会”,与全球各地的开发者协作,共同创新,创造出人们认为紧迫且相关的有意义的解决方案。该生态系统为开发者提供了必要的资源,使他们能够加入全球任何地方的 “BUIDL” 团队,解决引人入胜的问题;并在黑客松中与其他建设者一起感受到社区归属感;同时还通过激励机制推动他们实现有意义的目标,而这些目标往往又会引发更具挑战性和刺激性的下一阶段任务。Dora 生态系统创造了一个充满可能性的环境,使人们能够构建去中心化的产品与服务,例如将所有权交还给用户本人,增强他们在数字世界中的自主性、安全性以及对金融资产的控制力。正如下文将进一步讨论的,大型企业和垄断机构通常并不会从这些类型的技术中直接受益。那么,他们又有什么动机去资助这类技术呢?开源技术栈能够提升价值的质量,因为它为人们提供了开发更具意义产品的路径,而这些产品通常比那些由大型、目标狭隘的机构所产出的产品更具意义。
因此,如果自动化有可能减少甚至消除人们运用能动性、获得自我效能感的“质性丰富机会“,那么它所腾出的空间,理应由其他在质性上更丰富的机会来填补。如果确实存在“人性”这样的东西,而这种人性包含了一系列需要被发展、以使人得以过上有尊严生活的能力,那么最优与最值得追求的政治与社会安排,应当是将“质性丰富机会”公平分配,以确保人们有选择去运用自身能力、成为能够良好运作并实现繁荣生活的个体。为人们提供质性丰富机会,使他们能够加以利用,并据此组织、调动并集中自身内在力量于那些能够锻炼与激发个体能力的实践之上,这就构成了一个让人过上更有意义人生的基础。它是给予人们成为他们所珍视之人的自由。
接下来的部分将转向对 AI 垄断企业的讨论,揭示它们是如何压制上述这类未来机会的。
Part 3
Section 3.1
人工智能领域中潜在的垄断者不言自明:谷歌、苹果、微软、Meta 和亚马逊。这些公司以及少数其他企业在 2024 年占据了 65% 的固定网络流量和 68% 的移动网络流量[27]。谷歌大约占据全球约 90% 的搜索市场,其品牌名几乎已成为“搜索”行为本身的代名词;Meta 拥有主要的社交媒体平台,如 Instagram、Facebook 和 WhatsApp,这些都是人们日常交流与信息分享中访问量极高的平台;微软控制着大约 72% 的桌面操作系统市场;在美国,苹果约占据 60% 的智能手机市场份额;而亚马逊则主导了线上零售,其规模“超过美国排名其后的 15 家最大电商零售商的总和”[28]。此外,谷歌、Meta 和亚马逊合计占据了美国约 60% 的广告收入。我们在网上所接触到的产品、精美广告、以及注意力的买卖,主要都是由这几家大型科技公司驱动的。根据 Synergy Research [29]的研究,到本世纪末,微软、谷歌和亚马逊三家公司可能将掌握全球高达三分之二的数据份额。这些公司还控制着大部分云基础设施——亚马逊、微软、谷歌(以及阿里巴巴)合计拥有全球 67% 的云计算市场份额[30]。
这些公司拥有庞大的资源储备,同时也长期以来采用各种手段排挤竞争对手,包括通过并购消灭潜在威胁、利用市场主导地位优先推广自家产品、实行掠夺性定价、利用网络效应,以及其他众所周知的策略。例如,鉴于亚马逊在电子商务领域的市场主导地位,它可以通过优先推荐自家产品,排挤其他可能品质更高的供应商产品。消费者在面对价格更低的亚马逊产品时,往往更倾向于购买,而亚马逊正好拥有充足的资源来维持这种低价策略。在网络效应方面,“目前[31]大多数科技巨头的用户数量都以十亿计”,这为初创企业和小公司制造了几乎无法跨越的障碍。而谷歌也多次被指控故意降低某些内容的排名,并优先展示有利于自身利益的信息。
[27] https://www.applogicnetworks.com/blog/sandvines-2024-global-internet-phenomena-report-global-internet-usage-continues-to-grow [28] https://www.emarketer.com/learningcenter/guides/amazon-revenue/ [29] https://cxotoday.com/news-analysis/big-tech-to-own-two-thirds-of-world-data/#:~:text=Without%20sounding%20like%20a%20predictor%20of%20doomsday%2C,data%20centers%20while%20the%20rest%20is%20on [30] https://botpopuli.net/digging-deeper-assessing-big-techs-capture-of-the-internets-infrastructure/#:~:text=The%20dominance%20of%20Big%20Tech,Services%20(AWS)%20in%202006. [31] https://academic.oup.com/policyandsociety/advance-article/doi/10.1093/polsoc/puae012/7636223
如今,这些公司正积极争夺对人工智能发展的主导权。“Meta、微软、亚马逊和Alphabet 预计在2025年将累计投入高达 3250 亿美元的资本支出与投资……相比这些公司在2024年报告[32]的约 2230 亿美元,这相当于增长了 46%。”此外,“几乎没有例外,所有初创公司、新进入者,甚至 AI 研究实验室都依赖这些大型科技公司:他们依靠微软、亚马逊和谷歌的计算基础设施来训练系统,也依靠它们庞大的消费市场渠道来部署和销售 AI 产品[33]。”科技巨头垄断了初创公司赖以生存[34]的关键资源——人才、数据和算力。
[32] https://finance.yahoo.com/news/big-tech-set-to-invest-325-billion-this-year-as-hefty-ai-bills-come-under-scrutiny-182329236.html [33] https://www.technologyreview.com/2023/12/05/1084393/make-no-mistake-ai-is-owned-by-big-tech/ [34] https://academic.oup.com/policyandsociety/advance-article/doi/10.1093/polsoc/puae012/7636223
现有的行业巨头正在开发各种模型,以维持其在各自市场中的立足点。由于它们掌握着大多数资源——例如,“这些公司贡献了标普500指数公司市值的 22% 以上,其单独市值甚至超过了加拿大、意大利等[35]部分 G7 国家 GDP”——它们可以随意挤压竞争对手,阻止初创企业和小型公司进入市场。正如前文所述,随着 DeepSeek 在全球市场中作为竞争者不断取得进展,这些最大规模的 AI 公司正在大肆渲染一场“军备竞赛”,并夸大中国威胁以及人工智能可能带来的危害,从而推动对 AI 的监管和开发限制,而这些限制最终最有可能使它们自身受益。与此同时,由于垄断体制依赖于专有模型,其架构、权重、学习算法、代码以及内嵌目标都对公众隐蔽不明,在 AI 渗透信息网络的过程中,这些公司的经济与市场主导地位也将以一种“隐秘的方式”塑造人们的思维和行为。
[35] https://academic.oup.com/policyandsociety/advance-article/doi/10.1093/polsoc/puae012/7636223
那么,监管是否能解决这个问题呢?《麻省理工科技评论》最近指出:“监管或许有帮助[36],但政府政策最终往往加固了这些公司的权力,而非加以削弱——这些公司能够利用其资本与政治影响力来操控政策。”亚历克斯·蓝姆佩尔(Alex Rampell)[37]最近写道[38]:“拜登政府发布了一项行政命令[39],试图以人为设定的门槛限制计算能力,禁止开源技术,理由是其对国家安全构成威胁,同时这实际上为几家最大公司垄断监管资源敞开了大门。”例如,尽管萨姆·奥特曼在与贝利·韦斯(Barry Weiss)[40]的《自由新闻播客》(Free Press podcast)中否认了这一说法,投资人马克·安德森却一再警告称,拜登的 AI 行政命令的真正目的在于将 AI 的控制权交到少数几家公司(极可能是 OpenAI)手中,并通过提高市场准入门槛来消除竞争者。此外,尽管此举颇具争议、甚至可能显得天真,自从 DeepSeek 发布其 V1 和 V3 模型以来,Anthropic的 CEO 达里·阿摩地(Dario Amodei)一直呼吁加强出口管制政策[41],进一步限制中国获取芯片的能力。然而,正如迪伦·潘特(Dylan Patel)[42]和纳森·兰伯特(Nathan Lambert)[43]在 《莱克斯·弗莱德曼博客》中指出的那样,DeepSeek 的开源模型显然并不构成任何实质性的国家安全威胁。但它确实对那些依赖专有系统、通过模型控制潜在价值的生态构成了威胁。DeepSeek 的方法迫使这些“专有资本”朝着可被任何人使用与构建的公共资源方向转化。正因如此,阿摩地对“单极 vs. 双极世界”的坚持背后其实包含着竞争性的动机:要么 AI 权力集中于美国,要么中美都拥有对等的 AI 能力——而后者,在阿摩地看来,是必须避免的局面。
[36] https://www.technologyreview.com/2023/12/05/1084393/make-no-mistake-ai-is-owned-by-big-tech/ [37] 硅谷知名投资人,安德森·霍洛维茨基金(Andreessen Horowitz,简称a16z)的普通合伙人(General Partner)。 [38] https://a16z.com/why-deepseek-is-a-gift-to-the-american-people/ [39] https://www.federalregister.gov/documents/2023/11/01/2023-24283/safe-secure-and-trustworthy-development-and-use-of-artificial-intelligence [40] 美国著名记者、专栏作家,独立新闻平台自由新闻(The Free Press)的创办人。 [41] https://darioamodei.com/on-deepseek-and-export-controls [42] 半导体行业分析师,SemiAnalysis网站创始人。 [43] AI研究员、工程师。
或许,我们应当持有一种不那么鹰派的乐观态度。经济学家泰勒·科文提出了充分理由,认为与其全面投入一场军备竞赛,不如在相互合作[44]与共赢中寻找发展路径。当然,竞争仍然是必要的,但推动未来事件进程的竞争心态,不应仅仅源于达尔文式的“适者生存”逻辑,而应更接近尼采所观察到[45]的古希腊式“竞技”(Agon)[46]传统——那是一种社会制度,其中的艺术家、军事领袖与运动员通过竞争彼此激励、共同成长。
[44] https://www.youtube.com/watch?v=TcJtvzF-FP8&t=2736s [45] http://www.northamericannietzschesociety.com/uploads/7/3/2/5/73251013/nietzscheana5.pdf [46] https://en.wikipedia.org/wiki/Agon
没有对手,竞争者也将迷失方向。因为没有了改进、突破和创新的机会,个体便失去了变得更好、更具创造力的可能。竞争者的存在本身就依赖于愿意对抗他们的人。正是因为有人挑战,希腊诗人才得以想象得更深远、表达得更出色。尼采指出,希腊竞技者面临的最大危险不是失败,而是——失去竞争对手。他写道:“这正是希腊竞技理念的核心:它厌恶独裁,畏惧其危险,它渴望用‘另一个天才’来抵御某一位天才的压倒性力量。”我们不应将竞争理解为自然状态下的求生挣扎,那种资源稀缺、人与人互为威胁的霍布斯(Thomas Hobbes)式处境——“孤独、贫穷、肮脏、残暴而短暂”[47]。我们也不应将竞争本能视为某种原始性冲动的残余,只为了压制对手、消灭威胁。我们应当将其理解为一种可以高贵化的本能,正如尼采所言,它是“所有人类情感、行为与作品的唯一丰沃土壤”。竞争本能自身也具有德性,应当被培养成“在正确的时间、以正确的方式、出于正确的理由”去发挥作用的东西(亚里士多德,《尼各马科伦理学》(Nicomachean Ethics)第二卷),而不是被视作一种必要之恶。阿摩地害怕中国,这可能不是正确的回应——或许,一个更好的、更具德性的回应,是将中国视为值得尊敬的竞争者。
[47] 霍布斯的《利维坦》(Leviathan)中对自然状态下的人的生活的刻画。
Section 3.2
现在让我们聚焦于这些潜在的 AI 垄断企业为何会通过主导 AI 生态系统,压制质性丰富机会的更广泛传播。原因至少有两个:第一个涉及经济能动性,第二个涉及价值能动性。所谓经济能动性,是指人们进入市场、创造能满足消费者需求与欲望的价值与效用的能力。如果市场上的 AI 模型被集中掌握在少数公司手中,新兴企业与创业者为世界做出有价值贡献的机会将受到限制。那些能够回应民主、医疗保健、金融自主、政治权利与自由,或其他重大而有意义问题的创新,将大幅减少,从而也会降低 AI 所可能带来的社会福祉。任何威胁到这些少数 AI 垄断企业的控制力、影响力或财富的产品与服务,将被直接排除在市场之外,而不是由市场自然机制或消费者的真实需求所决定。
另一方面,所谓价值能动性,是指人们有能力对社会应追求的目标产生影响、发表意见。如果 AI 是在不透明的条件下、依据无法被公众了解和介入的价值与目标进行训练的,那么人们在这些问题上的影响力就会被削弱。如果由专有模型决定大多数或几乎全部嵌入 AI 的产品与服务的性质,那么人们对这些技术的控制权将大为减少。例如,所谓“对齐问题”指的是如何使 AI 与人类的利益保持一致。那么,什么是人类的利益?什么是构成一个良好且值得追求社会的目标?AI 的运行应遵循哪些道德与伦理原则?这些价值是否可以由少数几家公司决定,而无需公开其训练数据与学习算法?是否可以不接受公众监督与介入?如果技术架构被封闭在公众视野之外,那么上述问题的答案就更有可能来自权威的决定,而不是通过民主程序获得的共识。
经济能动性与价值能动性的双重丧失是危险的,本文余下部分将进一步阐述原因。
Section 3.3: 经济能动性
正如奥地利经济学家路德维希·冯·米塞斯(Ludwig von Mises)与弗里德里希·哈耶克(Friedrich Hayek)所著名指出的,苏联之所以在某些方面具有毁灭性,部分原因在于它无法通过自然发生的市场机制来合理分配资源。在这样的体制下,由内部的中央计划者来决定人民的需求与欲望——而这些人所掌握的信息资源既稀缺、又充满偏见与误差,无法实现准确分配。因此,大量官僚主义和强制性的手段被实施来调配国家资源。
举例来说,国家必须设定价格。至少是在苏联的情况中,并不存在一个广泛可用的自由市场,来使商品与服务受到供需关系的调节。生产者依据国家命令进行生产,而非根据市场激励(如竞争)自行调整方向——这些激励本应协调生产与消费,促成市场均衡。换句话说,价格失去了其关键信息功能——它本应指示资源该流向何处。哈耶克在《通往奴役之路》(The Road to Serfdom)中写道:“任何对某些商品的价格或数量的控制,都剥夺了竞争协调个体努力的能力,因为此时价格变动无法反映环境中的相关变化,也就无法为个体行动提供可靠的指导。”
不过,对本文来说,更重要的是:国家控制的生产与经济计划还意味着人们被剥夺了进入市场并创造价值的机会,使他们难以通过创新改善自身生活。任何可能威胁国家权力、削弱其合法性与影响力,或转移其部分控制权的创新行为,都将被禁止进入市场。举个例子:假设某人观察到,在某国的偏远乡村地区,由于常年洪水泛滥,人们无法修建道路,从而难以参与国家选举。这位发明者研发了一种不受洪水腐蚀的新型混凝土,并希望在乡村修建道路,改善人们的通行条件,让他们更容易参与公共事务。但当他向国家交通委员会申请资源时,却遭到了拒绝。原因是:该地区居民普遍希望拥有农业生产的自主权,因此国家不愿意为这些人提供进入选举制度的通道。而在缺乏市场竞争的情况下,也没有其他机会和机制可以去建设这些道路。
垄断,尤其是在受到监管体系保护的情况下,构成了类似的威胁。马克思曾做出一个著名批评:资本主义作为一种社会制度,其内在逻辑会逐步而不可避免地导致生产资料向少数人手中集中。虽然包括哈耶克和米塞斯在内的许多经济学家认为这种看法是错误的,并坚信在正常运作的资本主义体系中,这一结果是可以避免的。但如果人工智能遭到垄断,那么马克思的预测将比以往更加接近现实——无论这是由于历史规律,还是由于无法预见的结构性变数所致。正如克里斯·迪克森(Chris Dixon)[48]在其著作《阅读、写作、拥有》(Read, Write, Own)中观察到的,初创公司之所以能在市场中找到生存空间,部分原因在于大公司往往目光短浅,无法及时察觉到新兴产品正逐步获得消费者的关注。在专注于自身业务的过程中,这些巨头常常错失市场趋势与动向,而初创企业若运气足够好,就能积累足够势能以形成竞争力。但如果这些老牌巨头掌控了人工智能,他们就可能利用 AI 的能力来抹平初创企业原本可以利用的那些优势。随着时间推移,垄断企业将对市场形成难以穿透的控制权,各行各业的价值链最终将进一步“上游集中”到这些公司手中——比现在更甚。由专家所忽视、却能在市场中创造出意想不到价值的颠覆性技术,其创新空间可能会被完全挤压出去。
[48] 安德森·霍洛维茨基金普通合伙人,负责加密货币与Web3投资部门(a16z crypto)。
由于人工智能具备智能能力,它作为资本工具拥有极大的潜力,能够创造出改善人类生活的先进技术。但,由于有些对公众最有益的应用方式,可能并不符合政府与大型企业的利益,其潜在福祉也就可能在权力结构中被悲剧性地削弱。其中最明显的例子就是金融自主权。
看看比特币的案例就足以说明问题。中本聪(Satoshi)[49]发明比特币的初衷,是为了让人们拥有金融自由的能力——通过创造一种稀缺资源,其价值储存功能可与黄金相类比。比特币使那些生活在高通胀、货币极度贬值国家的人们,能够积累具有全球流通性的财富。人们可以拥有一种不会因货币供应过量或国家财政赤字上升而贬值的资产。比特币能够帮助人们过上更加稳定、安全的生活,它提供了透明性、个人所有权,以及能够激励社会合作的制度安排——这一切都无需依赖强制性信任或道德施舍。
[49] 比特币(Bitcoin)的创造者,身份不明。
人们本希望掌权者能够设法将中本聪为世界带来的巨大价值纳入现有体系。并不是说比特币应立即取代法定货币,而是说,考虑到比特币在应对法币体系中潜在致命问题方面提供了极具前景的解决方案,政府至少应当付出更大的努力,将这些解决方案纳入实践。合理的期待是,执政者会寻求一种方式,将区块链、比特币及其增强经济自由的潜力加以整合。然而,直到最近,有关这一技术的监管进展一直缓慢而混乱。在拜登政府期间,由于政策缺乏清晰性与明确性,关于加密货币的许多举措都未能充分发挥其潜在价值,反而阻碍了其更高效、更具生产性的使用路径。
如果AI被通过监管框架实现垄断,那么那些原本有潜力改善人类生活的技术也可能轻易被弃置。若这些技术与政府或企业利益发生冲突,大多数人将无法通过授权或专利使用这些专有模型,而中小型企业也会被并购吸收。尽管人工智能本可以彻底革新选举平台及人们参与选举的方式;尽管它本可以通过更优的数据安全手段或创造更多经济机会来增强个体自由,但探索这些可能性的路径,若与掌控大多数 AI 技术栈(甚至全部)的公司利益不符,就很可能被封锁。如果某项潜在的 AI 技术有可能通过解决某些产业赖以牟利、甚至具有寄生性质的问题,从而威胁广告收入,那么像谷歌与 Meta 这样的科技公司几乎必然会阻止这一技术进入市场的尝试。
特朗普政府迄今为止最重要的政策举措之一,就是其新的加密货币政策。该政策废除了上一届政府的行政命令,并致力于制定一个有助于推动该技术发展的监管框架。这对于人工智能领域中正在发生的其他形式的创新具有重要意义。有了除了传统风险投资之外的其他资源——例如通证经济(tokenomics)[50],初创公司可以为其项目提供资金支持,并积累发展势能。
[50] 也译为“代币经济学”,是对加密货币或区块链项目的经济层面的研究和分析,尤其关注其原生数字代币的设计和发行。该术语由“代币/通证”(token)和“经济学”(economics)两个词组合而成。
彼得·蒂尔在其著作《从零到一》(Zero to One)中提出,初创公司本身就在、也应该在寻求成为垄断者。他们需要在市场中占据一个特定空间,通过开发专有技术击败其他竞争者,并进一步排除后来者进入该市场。正如蒂尔所言,如果企业不想成为失败者,这种策略是至关重要的。若他们希望获得投资者的关注,就必须采取建立垄断地位的路径。然而,借助通证经济以及其他与加密货币相关的机制,人们也有机会开发出有价值的技术,同时保留开源精神。在这样的机制下,合作与协作得以推动,同时也能获得支持增长所需的资金。
Section 3.4 价值能动性
经济能动性之所以被削弱,是因为市场中那些具备质感的价值创造机会正在减少,使个体难以通过创新与生产满足不断变化的需求与欲望。当 AI 技术栈被少数几家垄断企业掌控并主导整个生态系统时,即使有人识别出一个真正有意义的问题,并设计出强有力的解决方案,如果这不符合大型企业的利益,该方案也很可能无法进入市场。经济活动及其所带来的社会价值,不应建立在一套容许权力任意压制、扼杀对社会整体有益事务的权威机制上。那么,AI 垄断企业又是如何压缩人们在价值能动性上的“质性丰富机会”的呢?
如果雷·库兹韦尔的奇点理论及其相关预测哪怕部分属实——如果人类真的将与非生物智能融合,并生活在日益人工化的环境中——那么人工智能的垄断不仅不可取,而且可以说是一种反乌托邦式的局面。这种设想唤起了关于“技术霸主”的画面:他们主宰着人类社会,而人们要么沦为智能机器的奴工,要么则是舒适而满足地享受着智能繁荣所带来的物质成果。在这样的图景中,总有人必须开采矿物资源,而另一些人则消费着由此生产出的丰富商品与服务。但如果我们假设 AI 的发展会快到足以让智能机器人无需人力就能完成矿产开采工作,那最终所有人都会转变为纯粹的“消费者”。“在接下来的几十年里,”库兹韦尔预测,“几乎所有例行性的体力与脑力活动都将被自动化。”届时,唯有那些具有社交性、创造性、创新性或高度不可预测性的工作将对拥有相关技能与培训的人开放,其余人将大多成为消费者。而借助纳米机器人、虚拟现实、非生物智能增强技术与无处不在的信息流动,我们的现实将愈加接近哲学家罗伯特·诺齐克(Robert Nozick)所设想的“体验机”(experience machine)。
通过某种装置的介入——无论是接入某种模拟装置,还是完全沉浸于类似虚拟现实(VR)那样的数字化、信息化环境中——人们可以体验到他们所希望的任何事情。任何感官体验、情绪、思想或事件,都会随时向任何人开放,随时可供消费。一个人可以体验写出“伟大的美国小说”所带来的深刻满足,像苏格拉底[51]那样在雅典法庭上勇敢地对抗陪审团,或像拿破仑那样英勇地站在青翠的高岗上俯瞰敌军,也可以在模拟的攀登中登上珠穆朗玛峰,体会坚持不懈的荣耀与世界之巅的视野。重要的不是这些事件是否真实发生,而是有人“渴望”它,而它就会“存在”。在这样的图景中,人生的目标就是消费;而“道德生活”——值得追求的生活——则被定义为追求内部刺激的生活。外部世界、个体真实的存在状态将不再重要。一个人是否真实地勇敢、富有同情心、充满爱意、公正、虔诚、善良或邪恶——这都不再有意义。人们的兴趣与冲突将在人工体验的消费中得到调和。在一个“问题已被解决”的世界中,没有需要行动者去解决的具体问题,行动者也就变得可有可无;唯一需要的,是“消费”。
[51] 古希腊哲学家。
这种情境真正危险之处在于,垄断企业将完全掌控生成技术的算法,也即控制我们可接触的信息结构。信息将不断被嵌入到以消费为中心的环境中。理想情况下,人们应当拥有自由,做他们想做的事,以他们认可的方式生活。但人们“看待”世界的方式,他们建构现实的方式,他们所处的社会语境——都会被那些已经整合智能资本、成为未来唯一商品与服务生产者的公司所过滤与塑造。哲学家艾伦·布鲁姆(Allan Bloom)在其著作《美国精神的封闭》(The Closing of the American Mind)中写道:“每一个教育系统都有一个它希望达成的道德目标,并据此构建其课程。它希望塑造出某种特定类型的人。”人工智能的垄断企业将通过改造人的生存环境来塑造“人是什么”的意义,以符合其自身利益。而真正重要的那些事情——运用能动性、实现真实的自我效能感、发现自己在人生中真正珍视与渴望的事物、建构让现实更一贯、宜居和统一的人生目标等等的机会——将被被企业利益所强烈影响和操控。而这些利益,本质上是围绕经济增长与利润最大化构建的。
在诺姆·乔姆斯基(Noam Chomsky)[52]与爱德华·赫尔曼(Edward Herman)[53]合著的《制造共识》(Manufacturing Consent)[54]一书中,两位作者提出,美国媒体实际上是一种宣传工具,而非客观的信息来源(这一观点当时颇具争议,但如今已成为主流看法)。他们认为,这种宣传功能是通过一套“过滤模型”来运作的,该模型将信息作为输入,并为公众“福祉”完美制造出标准化的输出。而其中一些媒体过滤机制,正是今天科技巨头所采用的。第一个过滤器是媒体公司的规模、所有权结构及其以利润为导向的商业模式。这使得进入媒体市场所需的投资与准入成本变得高得惊人,从而使其他竞争者难以生存。法律制度被用来执行一系列标准,这些标准压制了初创公司与中小企业的发展;而政府补贴则倾向于支持那些与政府利益保持一致的媒体公司。第二个过滤器是广告收入。广告不仅提升了特定公司的利润,也让它们在竞争中占据优势。那些无法吸引广告支持的媒体来源往往被市场边缘化。在此过程中,那些资金雄厚的媒体公司为了争取广告商的“青睐”,被迫迎合股东所要求的持续利润增长。这意味着任何挑战企业利益的声音,都可能因营收减少而遭受惩罚,最终被逐出市场竞争。
[52] 美国教授和公共知识分子,以其在语言学、政治活动和社会批评领域的研究而闻名。乔姆斯基有时被称为“现代语言学之父”,他也是分析哲学的重要人物和认知科学领域的创始人之一。 [53] 美国经济学家、媒体学者和社会评论家。 [54] https://focalizalaatencion.wordpress.com/wp-content/uploads/2012/08/herman-chomsky-2002-manufacturingconsent.pdf
这两个过滤器,正是当今科技巨头在其平台上运用的机制。他们主导市场,并依靠广告收入获取惊人的利润。正如乔姆斯基与赫尔曼所指出的另一个过滤器——意识形态偏向,大科技公司同样如此。就像上世纪八十年代的主流媒体会大肆报道敌对国家的种族灭绝与谋杀,却对发生在美国“势力范围”如拉美地区的同类事件视而不见,大科技公司也会在符合其经济与利益考量时,沿着特定的意识形态线索行事。由于其庞大的利润模式与动机,大科技公司的利益并不必然与真理、勇气、准确性、诚实、公正或善恶标准一致。只有当这些价值可以带来可预见的利润与效用最大化时,它们才可能被采纳。因此,如果 AI 垄断企业逐步获得市场主导权,并以其最先进模型为基础将大量商品与服务推向市场,那么人们对于世界的理解、他们如何看待现实、哪些事物最值得关注——都会在信息过滤器的引导下被重塑。这些过滤器正是大科技公司用于“产出有利于技术发展结果”的机制的一部分。个体发展自身的机会、形成自我世界观的过程、以及构成生活统一性的价值体系,都将受到科技信息过滤器的支配与重构。
我们很容易想象这样一个世界:信息的生成由一小部分集中的模型主导,这些模型构建出一套相互交织的信息网络,强化着不准确、不诚实、甚至是伪造的信息结构。新闻标题与报道可能散布错误主张与对现实的歪曲,而这些说法又会被其他虚假信息源所“证实”,彼此互为支撑。这种信息结构——即信息的组织方式及其意义赋予机制——可能会被人为策划,以服务于掌握权力与控制信息传播资源者所设定的特定目的。少数人认为“最好的”内容将被优先推送,而公众的想法将逐渐变得从属,最终被操控以符合权力方的利益。这并不是在指责某个实体或个人有恶意意图,而是在强调这样一种结构性困境:当生成并传播社会所消费的信息的能力被集中在少数几方手中时,这种权力格局所带来的难以解决的困境。
这最终将不可避免地导向类似于前文提到的诺齐克“体验机”的世界。人们获得一种超越消费伦理的生活形式能力的机会将被极大压缩,甚至被彻底剥夺。确实,假设未来大多数工作被自动化,人们通过基本收入实现生活保障,那么个体将从劳作的束缚中解放,不再被迫为经济增长贡献劳动力。从某种意义上说,人类将获得对约束与必需品的自由。但问题在于,如果没有施展自由的媒介,如果没有真正的机会在具体经验中运用自己的能动性,那么这种自由就并不是真正的自由——至少不是那种更深层次的、积极意义上的自由。那种引导人们思考“如何生活”、那种通过探索而发现值得投入心力与时间的事业的过程、那种确立人生目标并在充满挑战与刺激的环境中努力实现的能力,将会在这样的结构中逐渐失效,甚至彻底被边缘化。
哲学家约翰·杜威(John Dewey)曾写道:
我们很少意识到,我们对什么有价值、什么无价值的判断,在多大程度上是受制于我们并不自觉的标准。但一般来说,那些我们未经思考便视为理所当然的事物,正是决定我们有意识思维与判断结论的关键。而那些位于反思之下的习性,往往正是在我们与他人的持续互动与交换中形成的。
如果构成社会的制度是由那些以提升股东利润为目的的大型企业所主导——这将在它们主导人工智能时成为现实——那么它们的模型将渗透进经济的每一个领域,渗入我们的环境。这些环境将影响我们所被激发的生活方式,朝向不再体现为实际的‘存在’(being),而是依赖于‘拥有’(having)。也就是说,什么是显著的、值得追求的、具有吸引力的,不再取决于它所需要的努力、它所要求的冒险精神,或它所能激发的成长过程,而是取决于它能否填满并打发时间。对于一种由消费伦理塑造的意识而言,显而易见、理所当然的东西,将与另一种由合作构成、旨在促使个体能动性寻求意义与目标的社会完全不同。前者会看到一个充满各种可能体验的世界,但这些体验除了即时呈现的感受之外毫无意义;而后者则仍然会体验到“必要性”,以及那种不可遏制的冲动——即人必须感受到世界上仍有值得行动之事。赫尔曼·梅尔维尔(Herman Melville)在其伟大的美国小说《白鲸》(Moby Dick)中写下了这样的句子:
我坚定目标的道路铺设着铁轨,我的灵魂被刻槽其上。穿越无底峡谷,穿越山脉深处与激流之下,我直奔而去!没有障碍,没有转弯,只有通向铁轨终点的直路!
但愿,那些曾赋予梅尔维尔写作力量的精神碎片,在未来的某个角落依然得以存在。
Section 3.5
在《查拉图斯特拉如是说》(Thus Spoke Zarathustra)一书中,尼采描绘了两种未来人类的形象:“末人”(Last Man)与“超人”(Overman)。这两者在本能、欲望、动机与驱力方面有着根本性的不同。他们所看到的世界、感知世界的方式也截然不同:哪些事物对他们而言是显著且有意义的,什么是“善”或“恶”,对自我与世界的信念与态度,皆南辕北辙。
尼采对“末人”充满蔑视,而他的理想目标则是“超人”。“末人”代表一种追求舒适、安逸与满足的生活方式——那是一种消费的生活,是一种被动的满足。末人的畜群(herd)沉浸在“白天的微小快乐、夜晚的微小快乐中,但极度重视健康。他们说:‘我们发现了幸福’,眨着眼睛”。这样的存在,培养出的是享乐、安逸、饱足与消费的本能。尼采常将这种状态比喻为“反刍的牛”。而“超人”则是那种能够保有创造与超越本能的存在,他将生命导向某个遥远而艰难的目标,借此创造出一种超出自身的价值,使生活因此获得尊严与意义。超人仍然保有那种穿越变革性经验的冲动,那种能改变自我存在状态与意识体验的本能。正是这种冲动激发个体去掌握现实、理解现实,并因此增强他们影响现实的能力——个体越来越能够通过自己的活动与存在方式去塑造经验,建构世界。“末人”的美德——最大化快乐并最小化痛苦,在“超人”看来,恰恰是堕落的恶德。
人工智能的垄断结构及其以利润为导向的模式,正在推动“末人”的出现;而开源则是在为“超人”保留空间。随着人工智能被集中于少数强权之手,并通过这些权力机构设定的参数向市场大量输出商品与服务,整个信息景观及其传播网络将被精心策划成一种伦理结构——这种伦理以最大满足与持续消费所带来的舒适感为核心。在这样的结构中,个体所接触到的机会与环境将不再是“质感质性丰富”的;它们不会激发人们内在的主动能力,而只会使人变得能够追求一种消费社会所设定的终极目标——即最大化产出与回报的路径。
而开源生态系统,则保留了一个人类能动性仍能找到出口的空间。在那里,创造力与创新的目标不再仅仅是为了逐利,而是为了实现一种更完整的人类生活。
现在,本文开篇提出的一个问题是:自动化是否能带来足够多的机会,使被替代的劳动力能够重新获得工作?到现在我们已经看到,黑客范式与开源生态系统的确让这一目标更为可行。彼得·蒂尔的《从零到一》可以说是一本创业者指南。而他在书中明确指出:创业的目标应当是至少模仿,并努力实现垄断。所谓“成功”,就是在某一市场领域内占据主导地位,排除其他进入者,并通过专属供应尚未满足的需求来实现利润最大化。但成功初创企业的统计数据[55]却令人沮丧。初创企业的失败率高达90%。在那些成功者中,首次创业者只占18%。获得风险投资资金的初创企业不到1%;获得天使投资的比例也不到1%;约有75%的初创公司依赖“信用卡债务、商业贷款与信用额度”来筹集资金。成功的几率微乎其微,而对那些敢于创业,尤其是技术驱动型创业者(这是失败率最高的一类)所需承担的门槛与风险,往往近乎不可逾越。蒂尔之所以鼓励初创企业采用垄断策略,部分原因正是因为唯有在获得足够稳固的市场地位之后,公司才终于能够喘息、拓展与创新。一旦达到垄断标准,企业便能掌控其特定领域(甚至是整个)市场中的价值输出——理论上,这会给企业与消费者双方带来好处。
[55] https://explodingtopics.com/blog/startup-failure-stats
然而,这种能力最终被集中在极少数能够侥幸成功的公司手中。一旦掌握了这种能力,它们便没有自利的动机去放手。而当某家企业依靠其垄断地位终于获得创新的自由之时,这种专属能力却也意味着其他拥有创造潜力的人被排除在外,仅仅因为他们没有获得那唯一的机会。
如果企业的成功几率更高,那无疑会更具吸引力。但传统的融资方式以及作为成功创业者所需经历的艰难过程,往往会打击甚至扼杀那些本有能力提出改变世界的强大创意的人们。而黑客范式之所以具有深远意义,正是因为它能够提供丰富的机会,让人们得以创造价值,而无需承担传统创业所附带的高风险。黑客范式的“北极星”之一,就是致力于打造一个开放的、无需许可的生态系统——一个充满机会、人们可以自由进入、自由利用关键技术信息,并能够与成熟企业协作,从而共同创造出更好、更具创新性的产品的环境。开放的生态系统能够赋予人们创造价值的可能,而封闭系统则将他人排除在外,关闭了协作的大门。
按照蒂尔模式的创业路径,那是一条崎岖不平的道路。它需要强烈的意志、非凡的创造力,当然还需要一定的运气。而这三者的完美契合,是极其罕见的。因此,真正能在创业中成功的人少之又少。通过一个无需许可的开源生态系统,通过减轻人们在创造有价值事物时所承受的沉重负担,我们可以释放出大量机会——这些机会无需你拥有成为乔布斯或贝索斯那样的雄心与资源,也不要求你必须独力成就一番技术帝国。事实上,那些科技巨头的成功,早已远远超越了他们当初想要创造创新科技的初衷。开源生态系统将推动科技进步的机会民主化,使人们能够真正参与其中,不必成为少数天才企业家的复制品。创新,理应是更具协作性、更广泛分布的,也应当距离普通人更近。黑客范式正在使这成为可能,它正在重构赛场的平衡。
或许,并不是每个人都想成为一名“黑客”。但开源为我们保留并拓展了一种最佳的原型模式,通过它,可以将具体的机会持续地、公平地分配给人们,让他们得以实践自己的能动性。正是通过拥有这类机会,人们仍能发现和体验到那种强烈的召唤感——“我必须去做某事”——即,一个目标的存在,使个体不得不相信,若忽视它,人生就将失去意义与目标。如果我们生活的世界中,人们能接触到的、最显眼且最具吸引力的事物,仅仅是尼采所说的那种“幸福”——那种不涉及个人牺牲、不包含作为德性的献身(devotion)、也无需为艰难而变革性的事业奋斗的意愿的“幸福”——那么这样的世界无疑比不上另一个世界:在那里,人们拥有真正的机会去成就伟大的事业,只要他们愿意去追求。
结语
当 IBM 的“深蓝”在 1997 年击败国际象棋冠军卡斯帕罗夫(Garry Kasparov)时,象棋并未因此被淘汰。人们依旧继续比赛,并不断变得更强。这一事实——即从那以后任何人类棋手都不可能战胜 AI 程序——并未动摇那些热爱象棋之人的热情与动力。那些献身于象棋的人依旧渴望打磨自己的技艺,学习更复杂的策略,在不断成长的过程中超越其他选手。象棋选手依然渴望变得更优秀,仅仅是为了变得更优秀。通过意志与投入实现成长,当他们登上新的水平时,那种深刻的成就感依旧真实而宝贵,尽管一台机器将永远是更强的选手。
在一部关于李世石(Lee Sedol)在 2016 年败给 AlphaGo 的纪录片中,有人说:“他在这台机器的对弈中获得了成长。他的人性在与这台无生命的创造物对局之后得到了拓展。而我们的希望,是这种机器,尤其是背后的技术,也能对我们所有人产生同样的作用。”还有人说:“或许 AlphaGo 能向人类展示一些我们从未发现过的东西。或许那是一种美。”如果被正确使用,人工智能可以拓展个体影响与改变世界的能力。它可以提供创造的机会,而非只是劳作的义务;可以唤起意义的体验,而非冷漠与疏离;可以使人获得一种有价值的自由,而非无所依托的自由。但这一切都取决于社会写作和去推动人们向值得努力实现的目标前进的环境;它也要求我们以不同的方式理解竞争。
Agency/Agent/Agentic/… 能动性 Being (以…方式)存在 Qualitatively Rich 质性(上)丰富 Open Source Ecosystem 开源生态系统 Proprietary 专有 Pleasure 快乐 Happiness 幸福 所有著作、节目与人物名称第一次出现标记英文原文。 除网站链接之外的脚注,均为译者补充;脚注中的外部链接为原文超链接的对应标记。 原文中的特殊格式均保留在中文对应词项中。
-
 @ bf47c19e:c3d2573b
2025-05-12 20:27:54
@ bf47c19e:c3d2573b
2025-05-12 20:27:54"Za sve one koji još uvek nisu u potpunosti razumeli kontroverzni Bitkoin, ovo je koncizni i informativni brzi kurs o novcu i kriptovalutama."
Bitkoin: Kraj novca kakvog poznajemo - IMDB
Prevod: SatoshiSan / @SSG_SatoshiSan
-
 @ 6ad08392:ea301584
2025-05-12 20:22:09
@ 6ad08392:ea301584
2025-05-12 20:22:09
Satlantis is here!
Well…sort of. It’s a little pre-mature, but it’s good enough for you to play around with. I wouldn’t necessarily call it super ‘useful’ right now but I wanted you to get an early glimpse into what we’re building so you can see how it evolves over time.
And besides - we have to release a first version at some stage!
Satlantis is the first travel-centric social network. It’s quite different from anything else that came before it. It’s part map, part directory, part events app and part social network.
It really is a monumental undertaking - but I’m convinced now is the time to build it. People are ready for something new. They are tired of the algorithmic slop social media has become. They’re craving real connection and they want to see, touch, smell, hear and taste the world. What better way to help them do that, than with a network that connects them, andhelps enhance their discovery of places, experiences and events that are relevant to them (based both on their interests and social connections).
That’s what this product is all about. We’re going to do what Google Maps, Yelp, Instagram, TripAdvisor etc. are all partially doing - but make it 10x better.
The first Satlantis app is now available on Apple Testflight or the Google Play store. In the coming month or two, we will make Satlantis accessible via invitation-only, to increase the quality of connection and discourse on the app, but if you’re reading this now, you’re in before we gate it, you can explore and give us some feedback while we work on it.
I will write release notes like this every couple weeks covering what we built, what to test and play with, what’s working, what needs improvement, what’s downright shit or broken and what’s coming in the next release. (This first one is the longest because I delayed it so much.)
I’d love to hear your feedback, and if you find this interesting, please share it around so other people find out about what we’re building!
The Good
Mobile AppWe got a version out, and you can actually use it.
Nostr Compatible.
Every single account on Satlantis is an nPub. You can log into Satlantis using your nSec (not your nPub - we forgot to include that...lol), and you will find your entire social network and all of your posts there (if they are media notes). On the Web, you need to use an extension, like Alby or Keys.band. On mobile you can paste your key (stored locally on the device).
Normie Friendly.
We also built a smooth non-nostr focused sign up flow. We originally used the nSec bunker, but that was a mess (love u Pablo). So we built our own nSec bunker, but that sucked too. Passwords are old school. After interviewing 100 people not into Bitcoin or Nostr, 95% of them preferred us to store their key. So…we took that feedback and created a really easy email + magic link, Google and Apple SSO sign up flow, that creates an account and Nostr keypair that we store on their behalf, encrypted.
If and when people work out what Nostr is and they want to take custody of their key, they will be able to export their key, and request deletion of their key from our DB.
Is this the most ‘pure’ solution? No. Does this mean they have to trust us? Sure. Could we do it better at some point? Yes, of course. But considering the number of mission critical features we need to build, we’ll come back to it later.
We currently only support Kind 1 events.
Well…we also support NIP-52 calendar events, but we’ve disconnected that for the time being because event organisers wanted co-hosts more than they wanted to broadcast their events on Nostr. We’re working on a way to reconcile the two. For now, post text & images. (Video coming soon).
Interest-centric onboarding.
We spent a lot of time building this. One of the key pillars at Satlantis is discovering people, places, events and content suited to you. As we dug down the personalisation rabbithole, we found that there is a resurgence of interest-selection in many apps: from Tinder to new apps like Locals and Timeleft. The more focused on personalisation the app is, the more in-depth the onboarding.
Of course Meta and TikTok do the best personalisation with their advanced ML & AI tools, along with their deep social graphs, but since we have neither (Nostr helps but it’s still very small), we needed a better way.
So we decided to build our interest-graph. It was brain-melting, but we developed a pretty exhaustive set of interests relevant to people in our target market. We then took that list and associated it to events, merchants, people, places, experiences, activities and content. We then built a whole new onboarding flow to capture this from new users, and associate it to their accounts. (Yes - at some stage, we’ll make this Nostr compatible so it can travel with nPubs)
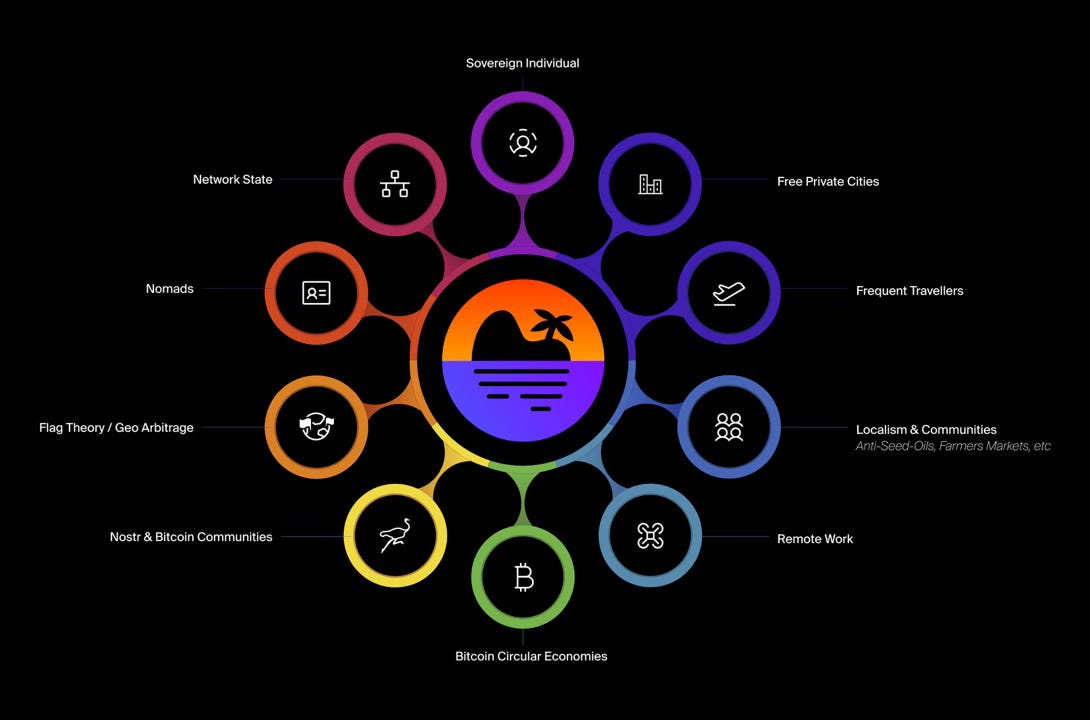 The net result is a base layer of insight we can use to help surface things that are of interest to users. Whether it’s an event, a place to eat, a gym or sauna, content to engage with or people to meet: like magic, things that are relevant to you will come to you.
The net result is a base layer of insight we can use to help surface things that are of interest to users. Whether it’s an event, a place to eat, a gym or sauna, content to engage with or people to meet: like magic, things that are relevant to you will come to you.Of course, in the long term we will use your social graph and the way you interact with content to do this - more like Meta and TikTok do - but for now, while the social graph is tiny, this is the most efficient and effective way.
Final word: the current version has all the interests - but it’s not very user-friendly. The latest design fixes that by grouping the interests into better subcategories. Keep an eye on that in a subsequent release.
New Merchant Discovery Experience.
This was also a monumental task. Our first merchant experience was just a shitty map with a list on web, and just a list on mobile (see below). This list was ranked by an “aggregate rating” we computed by analysing all the venue’s ratings from apps like Google, Trip Advisor and more.
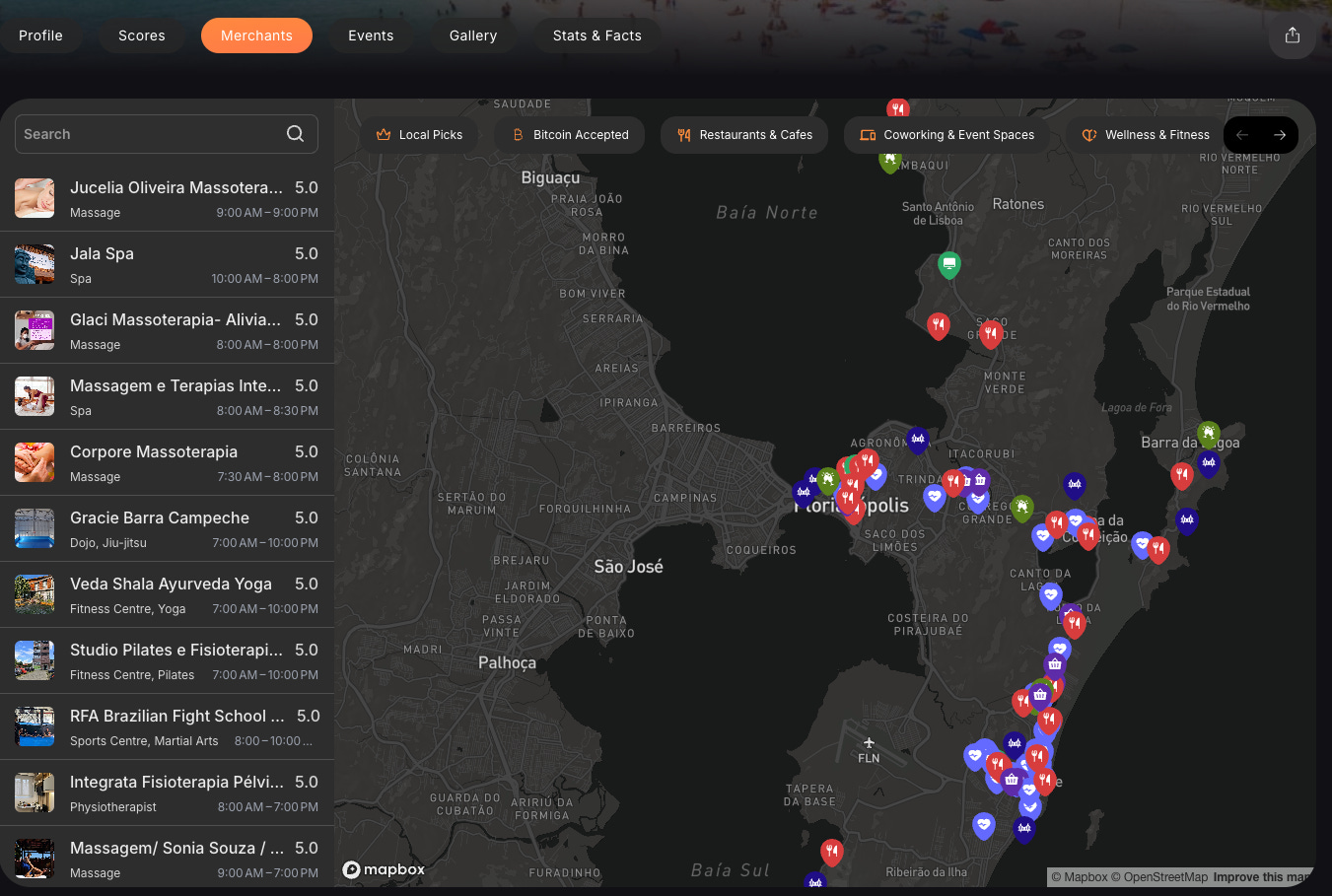
We spent a long time trying to figure out how to display this better and do it in a way nobody else is, because seriously -can you think of a single food app or merchant map out there which has a nice UI or UX? No.
AirBnB transformed the UI & UX for accommodation and pushed the whole space forward. Nobody has really done it for every other kind of place you go to. So we took it up ourselves to fix this and create a proper “merchant discovery experience” with an information-dense location tile. Check this out:
Notice how we managed to get all the key information you need about a place there on the one tile, including who in your social circle has recommended it. That’s the key ingredient which makes Satlantis special. No more messaging friends or people you know “hey - have you been to that place” or “do you recommend that place”?
 One small issue here is that this upgrade will kill the map…but only for a couple weeks, until we release the new map view!
One small issue here is that this upgrade will kill the map…but only for a couple weeks, until we release the new map view!Merchant coverage
Our merchant app covers SIX distinct categories:
-
Cafes & Restaurants
-
Health & Wellness (think Gyms, Spas, Saunas, etc)
-
Attractions (from Museums, to lookouts to beaches & hikes)
-
Grocery & Specialty Foods (think Organic food store, farmers markets, etc)
-
Coworking & Event Spaces
-
Nightlife (Bars, Clubs, etc)
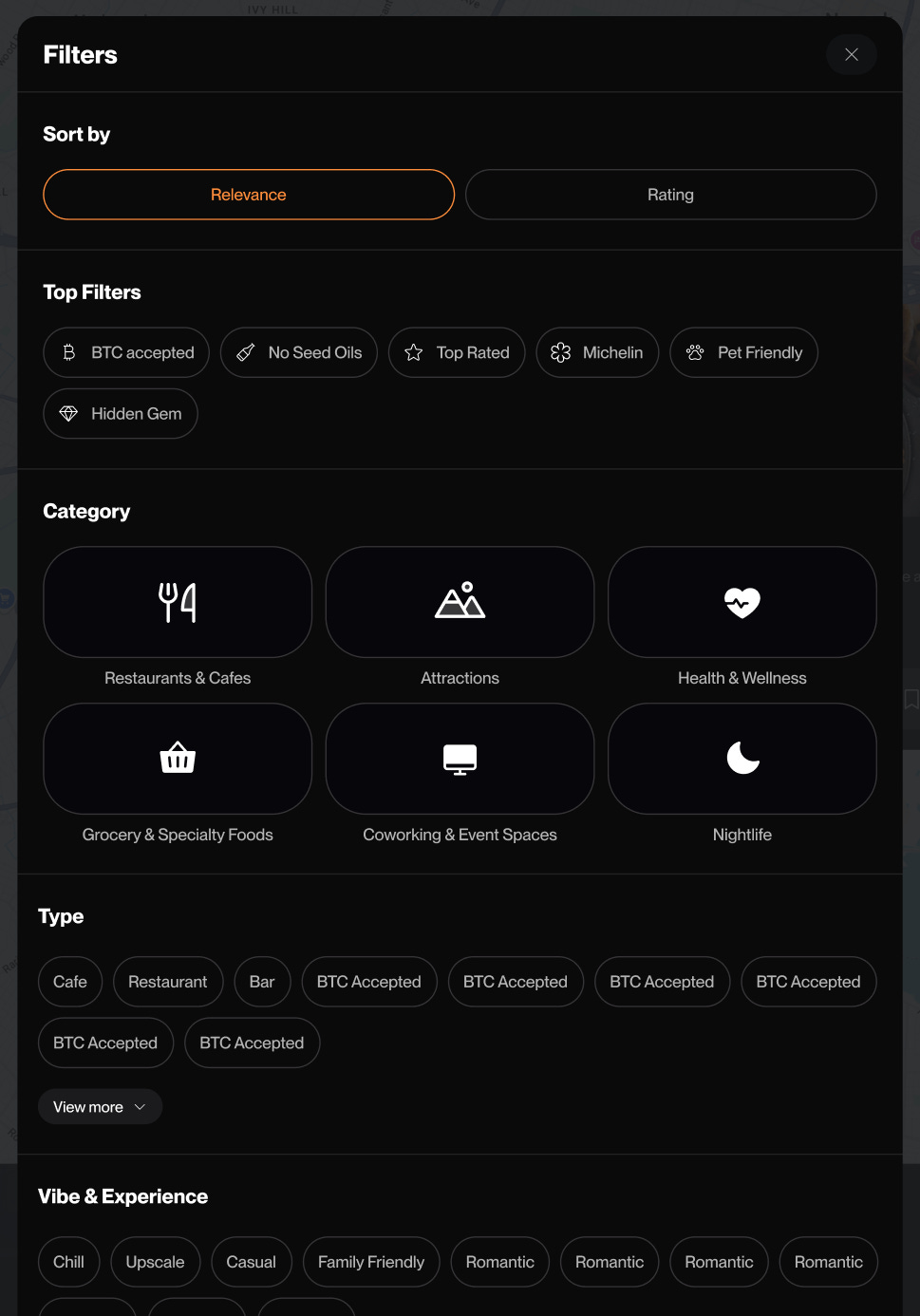 We scoured the web for the best curated lists and directories for each of these categories. This in Bitcoin accepted (everything relevant from BTCMaps - because we’re also built on Open Street Maps, so it’s synced up), Seed Oil Free (everything from Local Fats & Seed Oil Scout is here), Michelin Star rated, Real Milk (Raw Milk directory) and more.
We scoured the web for the best curated lists and directories for each of these categories. This in Bitcoin accepted (everything relevant from BTCMaps - because we’re also built on Open Street Maps, so it’s synced up), Seed Oil Free (everything from Local Fats & Seed Oil Scout is here), Michelin Star rated, Real Milk (Raw Milk directory) and more. Alongside all of these directories, our network of local ambassadors have submitted their top local picks for their favorite cities, so you have real local recommendations.
The destinations with the best maps are currently Canggu, Uvita, Prague, Sao Paulo, Dubai, Florianópolis.
Suggest Places & Merchants
This is working quite nicely. Anyone, anywhere can now suggest their favorite merchant. For now, we’re manually approving submissions daily to avoid spam and irrelevant shit. In time, we’ll find a better way to do this.
It’s all plugged into the Google API, so you can just type in the name of the place you think should be added (from mobile or web here). Once approved, our AI pipeline goes to work gathering all the available data from Google, TripAdvisor and elsewhere to set up the merchant profile, complete with review summaries, images, profile bio, contact details, opening hours, tags and more.
Got more upgrades to this flow in the works, but it’s ready for you to try out now.
City Pages
The current city pages are part of an outdated design which doesn’t fit our new visual language, but they are a ‘live’ feature. The original idea was to blend elements of Pinterest and Instagram but it backfired so we are changing to a more slick one-column feed. That being said, the core features of the city pages work. You can:
-
Join a city (like joining a community or following the page)
-
Post content on the city page
-
Navigate over to the different available pages, including merchants, events, scores and stats + facts
We have 80 cities currently available. More to come.
Scores, Stats & Facts
When we set out to first build Satlantis, we wanted to improve on the information NomadList was presenting for cities & destinations around the world. So we developed a different approach for city scoring based not only on data we could get from Numbeo, etc - but also information direct from people on the ground - in particular; expats and locals.
We put together a set of score categories and created a dedicated survey for select people to fill out, which would create some “foundation” scores, with a view to have this survey available to the crowd, perhaps via a score voting system or some sort on the page. We haven’t got that far yet. Right now, we have foundation scores for each of those 80 active cities, along with key Stats and Facts, like cost of living, wifi speed, water drinkability, and more:
This is not a core feature for us, so we will look to partner with other providers to enhance the experience, or we’ll completely re-think how we’re going to do it. Stay tuned for more here and let me know if you find it useful at all right now (or not).
Events
Last but not least, we have events! God dammit this was annoying because we built it NIP-52 compatible in the beginning, which then limited what we could do with co-hosts and other essential event features. And all for nothing since there are no other well built or maintained calendar-event clients on Nostr anyway.
So right now, when you post an event on Satlantis, it will post only on Satlantis. This means that as a host, you can edit, add co-hosts, add locations (proper merchant tiles) and delete.
We will make this Nostr-compatible again, most likely with some sort of button for hosts to “broadcast this event to Nostr” - knowing they will lose some flexibility once they do - but we need to do more research here. Maybe we’ll propose an upgrade to the calendar event NIP (or propose a new NIP altogether). It’s on our roadmap, so we’ll do our best to get to it soon.
Meetup integration.
We’ve been working with the Meetup API to let organizers quickly import their events into Satlantis. It’s been frustratingly complex because of how archaic they are, but we got it working!
🚀 If you run a Meetup, and want to automatically have your events listed on Satlantis when you list them on meetup,reach out! We’ll even cover the Meetup membership fee for 10 meetup groups who set up auto-importing for their events. If you’re interested, reach out to us.
The Bad
These things are currently bad, broken, incorrectly built or buggy. Believe me, if the list was exhaustive, this essay would be a book (our internal list is very full) - so I’m just going to touch on the main things we’re aware of and will be fixing…or just letting it burn slowly while we put out other fires.
Personal content feed
We started Satlantis with a media-only approach, taking inspiration from Instagram. We changed course a couple months ago to support text only posts, realizing there were a lot of other things people would like to post about travel, for example: guides, restaurants, reviews, tips, events, instructions, recommendations.
So…we started supporting this on the feed, and in the “post content” flow - but of course, not yet supported in the Profile view (which is still an image grid). This means if you post text only, you’re not going to see your own post on Satlantis 🤣🤣
To fix this, we’re building a “personal feed” section on your profile. But…that will come after we polish some of the things above, so if you’re posting on Satlantis right now, photos please!!
Video content
This one hurts too. We currently neither render videos from other clients, nor do we support video uploads on Satlantis. Not because we don’t want to, but because we haven’t got to it. This is high on the priority list and will be fixed in the upcoming releases.
Settings & Edit profile
We forgot to add “edit username” 🤣
This is being added now, along with a settings section where you can get your nPub and things like that. We’ll keep it very basic for now.
Notifications
Holy crap. These really suck. There is no other way to put it. The design is not great, the experience is buggy as hell and syncing notifications from the broader Nostr network doesn’t make life any easier. We’ll be making incremental improvements here (for a long time I guess).
Limited social graph functionality.
Right now, there’s not much social-dynamics beyond the feed. This will expand and begin to influence more than just content, but also merchants, events, people, activities, etc.
Speed issues.
Feed and profile loading times are sluggish and need performance improvements. Ongoing.
Large Destinations are problematic.
How do you rate a massive city like São Paulo as a single entity? Well….you can’t. Eventually, we’ll break major cities into regions, but that’s a big project for later.
For now, when you see scores, stats and facts, assume we’re covering the most relevant traveler-friendly areas (e.g., Jardins in São Paulo, Palermo in Buenos Aires, etc).
The Ugly
There is really only one new ‘feature’ to complete before we apply a feature freeze and continue on to polish everything. This and the other items listed will be available in the next release or two, so that the overall experience is a little more…beautiful.
Chat.
We wanted to do NIP-17, but considering that (a) most of the major apps are still NIP-04, (b) BTCPrague is around the corner and (c) limited resources, we chose to do a NIP-04 implementation for this first version. Not ideal, but good enough. Chat will continue to improve, not only with a NIP-17 upgrade, but with other features like chat folders, group chats, GIFs and more.
Polish List
-
Merchant Experience: Web and mobile updates
-
Merchant List: More cool places being uploaded
-
Events: New display, RSVP flow, co-host notifications, merchant integration
-
Onboarding: Updated interests tags & flow
-
Scores: Updates to Cost of Living & overall score weights
-
Notifications: A lot of improvement here
-
Feed: Text only posts, video uploads & rendering videos from other clients
-
City Page: New design and functionalities
-
Zaps: Yes. We will have Zaps.
Final Words
We have our work cut out for us!
We will be at BTCPrague in June and we are committed to releasing all of these features and components by then…as polished as possible.
The team and I have a couple of asks:
-
Download the app, and either create a new account or if you’re on Nostr, log in with your existing Nostr key (web requires an extension like Alby)
-
Go through the interests, and select those that are most relevant to you. The magic of the app happens as a function of how accurately you select those.
-
Post some content! Could be a photo introducing yourself or a “Good Morning” or whatever. Make sure you tag @Satlantis or @Svetski and I’ll boost you.
-
Check out the merchants in the top cities & see what’s around. The city with the most merchants right now is Florianopolis, but we have some coverage in many other cities
-
If you run a meetup or attend a regular Bitcoin meetup, let the organisers know, and let’s start to bring meetups and events across. Not asking anyone to ‘leave’ meetup now, but come and sync up your account so events are auto-published. \ As we make the events feature more robust (and Bitcoin native), every Bitcoin meetup in the world is going to want to come use this. If you’re early, you can help us shape it!
-
Let a couple of friends know about the app - ideally those who are not yet on Nostr - and ask them to try it out. They can sign up with email or SSO if they’re afraid to store their own key.
-
Like I said in the beginning, at some point in the next month or so, it will become an invite-only app. We will grandfather all existing users in, but new people will need an invite code (from existing users or via codes I drop into release notes and articles) to access it. \ \ The goal of this approach is to (a) increase the quality of connection amongst people on Satlantis, and (b) try a new way of growing a Nostr-based app.
-
Finally…we’ve decided to do an equity crowdfund. So if you find what we’re doing interesting and want to be a part of it, you’ll have a chance from June onwards. More to follow on this in the coming weeks. It will be on Timestamp Financial - Bitcoin crowdfunding platform - so go check them out.
Thank you again for your attention - I do not take it lightly. This is just the start, so expect to see ALOT more from us in the way of updates and shipping (plus these updates will be shooter).
Make sure you subscribe to this newsletter if you’re reading on Substack, or follow me if you’re on Nostr, Medium or wherever else you’re reading it.
Aleksandar Svetski
Thanks for reading Social 2.0! Subscribe for free to receive new posts & stay up to date with what we’re building & learning along the way.
When the app goes into “Invite Only” mode, you will need a special invite code to access it, unless you’ve already got an account. For now, it’s open access.
If you're already on Nostr, you're already on Satlantis. Just use an extension to securely log in with your nSec (on web), or with your nSec on mobile.
-
-
 @ 6c05c73e:c4356f17
2025-05-12 20:05:36
@ 6c05c73e:c4356f17
2025-05-12 20:05:36Já pensou em investir no Brasil, mas se sentiu intimidado pela volatilidade da Bovespa e as notícias de escândalos? E se eu te dissesse que existe uma maneira de expor seu portfólio ao mercado brasileiro, investindo em dólar, diretamente da bolsa de valores de Nova York?
Bem-vindo ao mundo do EWZ, o ETF (Exchange Traded Fund) que replica o índice MSCI Brazil 25/50, oferecendo uma janela para as maiores e médias empresas do Brasil. Se você está buscando diversificar seus investimentos e explorar mercados emergentes, o EWZ pode ser a sua resposta.
O Que Exatamente é o EWZ?
O EWZ é o ticker symbol do iShares MSCI Brazil ETF. Pense nele como um pacote de ações brasileiras negociado na bolsa de valores americana. Ele espelha o desempenho do índice MSCI Brazil 25/50, o que significa que, ao investir no EWZ, você está, indiretamente, investindo em uma cesta diversificada das principais empresas do Brasil.

Por Que Investir no Brasil via ETF?
Você já pensou em investir no Brasil? Mas ouve sempre falar desses riscos da Bovespa e vários escândalos?
Portanto, saiba que existe uma forma de investir no Brasil em dólar. Usando a bolsa de valores de Nova Iorque. Isso mesmo, você pode abrir uma conta em corretora estrangeira e investir no Brasil via ETF.
O ETF que replica a Bovespa (Bolsa de valores de São Paulo) é o EWZ. Esse índice replica o Ibovespa e reflete nele o peso das maiores empresas brasileiras, tais como:
- Diversificação em Dólar: Invista em empresas brasileiras sem precisar se preocupar com a flutuação do real. Seus investimentos são feitos em dólar, protegendo você das variações cambiais.
- Acesso Facilitado: Negocie o EWZ diretamente da sua corretora americana, sem a necessidade de abrir contas no Brasil ou lidar com burocracias locais.
- Diversificação Instantânea: Ao comprar EWZ, você está comprando uma fatia de várias empresas líderes no Brasil, reduzindo o risco de concentrar seus investimentos em uma única empresa ou setor.
Números Que Falam Por Si
Vamos aos dados concretos que mostram a solidez do EWZ:
- Taxa de Administração: 0.59% a.a.
- Patrimônio Líquido Sob Gestão: $3.6 bilhões em ativos. Isso indica uma boa popularidade do ativo.
- Volume de negociação diário: Em média $24 milhões, o que garante boa liquidez e baixas taxas.
- Dividendos: 7.33% a.a. Distribuído semestralmente.
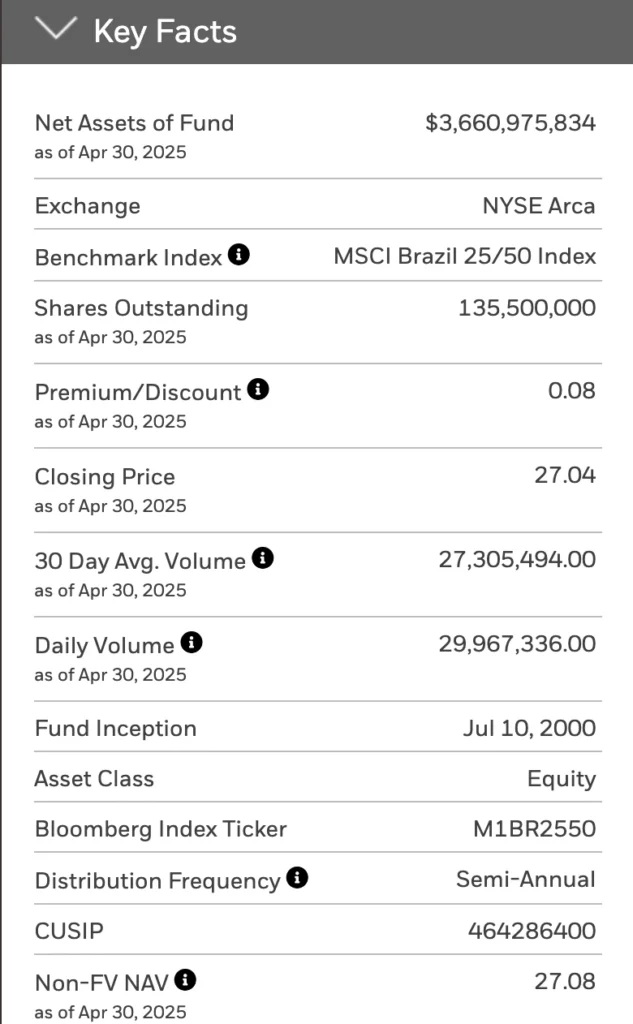
Qualitativo
- Com mais de 200 milhões de habitantes, o Brasil tem um dos maiores mercados consumidores do mundo. Isso representa uma demanda interna robusta e potencial para uma vasta gama de produtos e serviços.
- O país é extremamente rico em recursos naturais, incluindo minérios (ferro, bauxita, etc.), petróleo, gás natural e vastas áreas agricultáveis. Além disso, tem um potencial enorme e já desenvolvido em energias renováveis (hídrica, solar, eólica, biomassa).
- O Brasil é um líder global na produção e exportação de diversos produtos agrícolas (soja, milho, café, açúcar, carne bovina, frango). Há contínuo potencial para ganhos de produtividade e agregação de valor na cadeia.
- O Brasil desenvolveu um ecossistema de startups vibrante, especialmente no setor de fintechs, onde é referência global em inovação (ex: Pix, Open Banking). Há também crescimento em agrotechs, healthtechs e outras áreas. O grande mercado consumidor digital impulsiona esse setor.
Técnica
- O ativo teve uma queda vertiginosa. No entanto, desde Dezembro de 2024 vem apresentando uma melhora no comportamento. Isso, pode sugerir que há uma boa margem para comprar com "desconto". Visto que, o volume comprador tem sido intenso desde o inicío de Abril de 2025.

FAQ
O que significa a sigla EWZ?
A sigla EWZ é o ticker symbol (código de negociação em bolsa) do iShares MSCI Brazil ETF.
Portanto, EWZ não é uma sigla de um nome por extenso, mas sim o código usado para identificar e negociar este fundo específico (ETF) nas bolsas de valores dos Estados Unidos (como a NYSE Arca). Este ETF busca replicar o desempenho do índice MSCI Brazil 25/50, que representa as maiores e médias empresas brasileiras.
Qual é a composição do EWZ?
AS 10 Maiores Posições (na data de hoje):
- Nu Holdings (NU): \~9.3% - 9.8% (Setor Financeiro)
- Vale (VALE3): \~8.5% - 9.5% (Setor de Materiais)
- Itaú Unibanco (ITUB4): \~7.9% - 8.6% (Setor Financeiro)
- Petrobras PN (PETR4): \~6.2% - 8.0% (Setor de Energia)
- Petrobras ON (PETR3): \~5.5% - 7.3% (Setor de Energia)
- WEG (WEGE3): \~3.9% - 4.2% (Setor Industrial)
- B3 (B3SA3): \~3.4% - 3.7% (Setor Financeiro)
- Banco Bradesco (BBDC4): \~3.0% - 3.6% (Setor Financeiro)
- Ambev (ABEV3): \~2.9% - 3.4% (Setor de Consumo Essencial/Staples)
- Sabesp (SBSP3) ou Eletrobras (ELET3): Geralmente na 10ª posição, com peso entre \~2.5% - 2.8% (Setor de Utilidade Pública)
Sobre nós
Investir não precisa ser um bicho de sete cabeças! Na Threedolar, democratizamos o acesso ao mundo dos investimentos, oferecendo conteúdo claro e prático. Comece hoje mesmo a construir seu futuro financeiro!
Disclaimer
Nada do que eu escrever aqui é recomendação de investimentos ou chamada para compra e venda. Tire suas próprias conclusões e veja o que é melhor para você. Resultados passados não são garantia de resultados futuros. Cuide do seu dinheiro, pois ninguém o fará para você.
Referências
-
 @ 68768a6c:0eaf07e9
2025-05-12 23:58:56
@ 68768a6c:0eaf07e9
2025-05-12 23:58:56What Is Bitcoin? Bitcoin is the world’s first decentralized digital currency—created in 2009 by an anonymous person (or group) under the name Satoshi Nakamoto. Unlike regular money, it’s not printed or controlled by any government or bank. Instead, it runs on a global network of computers using a technology called blockchain. Why Is Bitcoin Valuable? Bitcoin is often called “digital gold” because it’s limited in supply—only 21 million bitcoins will ever exist. This scarcity, combined with increasing demand and global adoption, makes it valuable. Many people invest in Bitcoin as a hedge against inflation or unstable currencies. How Can You Use Bitcoin? Today, Bitcoin can be used for: Online shopping (some stores accept it) Transferring money across borders Investing for long-term growth You can store it in a digital wallet and send it anywhere in the world in minutes—with low fees. The Risks and Rewards Bitcoin prices can go up or down quickly—it’s very volatile. But many investors believe it will grow in value as the world becomes more digital. Tip for Beginners: Never invest more than you can afford to lose. Start small, learn as you go, and stay updated. Final Thoughts Bitcoin is more than just internet money—it’s a revolution in how we think about value, privacy, and freedom. Whether you’re a curious beginner or a savvy investor, understanding Bitcoin could be your first step toward financial innovation.
-
 @ 9c9d2765:16f8c2c2
2025-05-12 23:52:29
@ 9c9d2765:16f8c2c2
2025-05-12 23:52:29CHAPTER SEVENTEEN
"I don't get it... How is James still in charge?" Tracy murmured, her brows furrowed as she stared at her screen. She sat in her office, fingers nervously drumming against her desk.
Across from her, Mark stood with arms folded, pacing slowly. "You mean after all that evidence? After the blacklist, the embezzlement records nothing happened?"
Tracy shook her head. "Nothing. I checked again this morning. He’s still listed as President of JP Enterprises. It’s like the files we found didn’t even exist."
Helen, who had been silent until now, hissed through clenched teeth. "This is ridiculous. Are you sure the information got to the right hands?"
"It did," Tracy insisted. "I sent it directly to the Prime Minister's inbox using a confidential channel. I even received a delivery confirmation. Someone higher up must’ve swept it under the rug or maybe James covered his tracks faster than we imagined."
Mark slumped into the chair, clearly defeated. "He’s not just lucky he’s smart. Smarter than we gave him credit for."
For the first time since they began scheming, their confidence had begun to falter. They had dug into James’s past, unearthed the most damning of records, and yet… nothing. He remained untouched. Unshaken.
James continued to lead JP Enterprises with iron resolve, his status not just preserved, but strengthened. Whatever scandal they tried to ignite had fizzled out before it could burn.
The silence from JP's top board members was loud. No statements. No investigations. Not even a whisper of an internal review. To the outside world, James remained the unshakable President who had pulled a crumbling empire back from the edge.
Mark clenched his jaw. "He must have allies who are protecting him."
Helen nodded slowly. "We underestimated him. That was our biggest mistake."
Tracy remained quiet, her eyes still fixed on the screen as if trying to decipher what had gone wrong. She had risked everything, accessed confidential files, and violated protocols, expecting James to crumble.
Instead, he was thriving.
"Have you heard?" Robert leaned over his desk, eyes wide with interest. "JP Enterprises is about to celebrate their sixteenth anniversary. It’s going to be the biggest corporate event of the year."
Christopher looked up from the documents he was reviewing. "I heard. Mr. and Mrs. JP are returning for it. The entire business world is going to be there including us."
Robert nodded. "Every major company in and out of the city has received an invitation. It’s not just a celebration, it's a power show. A way for JP Enterprises to remind everyone who’s at the top."
Indeed, the buzz around the sixteenth anniversary of JP Enterprises was like nothing the city had seen in years. Massive banners were already being hoisted across the city skyline. High-end hotels were fully booked. Fashion designers, chefs, tech specialists, and media crews from around the world were preparing for the grand occasion. It was more than a business event, it was a spectacle.
At the heart of the preparations was James, the young and surprisingly unshakable President of JP Enterprises. Under his leadership, the company had grown in power and reach, and the anniversary was both a celebration of its legacy and a testament to its transformation.
Meanwhile, at Ray Enterprises, tension brewed behind the scenes. Though they were invited, the Ray family carried mixed feelings about attending the event. Memories of humiliation and disbelief still lingered the day James had revealed himself as the President was still fresh in their minds.
"We have no choice but to attend," Helen muttered in frustration during a board meeting. "If we stay away, we’ll seem petty and afraid. But going there means bowing our heads to him again."
Sarah, the secretary, tried to mask her discomfort. "It’s a corporate event, ma’am. It might be best to appear neutral… diplomatic."
Rita, now reinstated as General Manager, remained quiet but observant. She knew better than anyone how unpredictable James could be when it came to public appearances. She had no idea what to expect from him at the anniversary.
Back at JP Enterprises, preparations continued in full force. The guest list included billionaires, global CEOs, high-ranking politicians, and the most influential figures across industries. Red carpets would roll out, cameras would flash, and speeches would echo through the grand hall like music from an orchestra.
The city, already buzzing with excitement, awaited the grand event.
"I can’t believe it," the young woman muttered as she stared at her phone, her hands trembling with excitement. "James… the same James who used to sleep in front of Mr. Kola’s grocery store? He’s the President of JP Enterprises now?"
Her name was Evelyn. Sharp-tongued, impatient, and fueled by bitter memories, she had known James during his hardest days on the streets, days when survival meant fighting for leftovers and sleeping on cold sidewalks. To her, his rise wasn’t a success story to be admired. It was a jackpot she felt entitled to.
Storming into the JP Enterprises headquarters during working hours, Evelyn ignored the receptionist's polite inquiries and pushed her way toward the executive wing.
"I want to see James!" she shouted, causing heads to turn in the busy lobby. "I know he’s here. Tell him Evelyn from the street is here!"
Security was alerted immediately, but by then, Evelyn had already reached the waiting area outside the President’s office.
James, who was in a brief meeting with department heads, heard the commotion and stepped out with a composed expression. As soon as his eyes met Evelyn’s, something shifted. He recognized her instantly.
"Evelyn?" he said, frowning slightly. "What are you doing here?"
"Don’t act like you don’t know me, James," she snapped, crossing her arms. "You owe me. We suffered together. I was there when you were nothing. Now you’re swimming in wealth and you think you can forget the people who once mattered!"
James’s expression hardened.
"This is not the place for this kind of talk. You’re disrupting my company’s operations. If you need help, there are proper channels"
"To hell with proper channels!" she yelled. "I came to get what’s mine!"
That was enough. James turned to the nearby security officer. "Escort her out. And make sure she doesn’t return without a valid appointment."
The security guards moved quickly, but Evelyn didn’t go quietly. She shouted all the way to the exit, throwing insults, struggling, and drawing even more attention.
Among those who witnessed the scene was Tracy. At first, she thought it was just a random case of disturbance by some unruly visitor trying to make trouble. But as she watched James’s calm yet stern expression, and the woman’s emotional outburst, something clicked in her cunning mind.
This is gold, she thought, quickly pulling out her phone and snapping a series of pictures from the hallway James arguing with a ragged woman, the woman being dragged out, and James watching in silence. What a perfect way to ruin his reputation.
Tracy, ever the opportunist, reviewed the photos and smirked.
This is it… this will shake him up.
Without hesitation, she sent the pictures to Helen and Mark, attaching a voice note.
-
 @ a296b972:e5a7a2e8
2025-05-12 16:52:30
@ a296b972:e5a7a2e8
2025-05-12 16:52:30Wo sind der 1. Stock, das Erdgeschoss und der Keller? Das Dach ist noch zu bauen. Das Haus zum unerklärlichen Krieg ist unfertig. Der Bau wurde schon viel früher begonnen, aber die westlichen Medien behaupten das Gegenteil oder verschweigen es. Eine Vorgeschichte darf es nicht geben.
Am Ukraine-Krieg sieht man, dass ein Konflikt, der entgegen den Behauptungen der Propaganda-Maschine nicht erst im Februar 2022 angefangen hat, wie lange es dauert, bis wieder Verhältnisse zustande kommen, die eine Befriedung ermöglichen. Das Ringen darum ist hoffentlich endlich in die Zielgerade eingelaufen und man findet besser gestern als heute eine Lösung. So viele Menschenleben auf beiden Seiten hat dieser Wahnsinn bislang gekostet. Am Ende, wofür? Die Verwirrung bleibt bis zuletzt, denn einerseits treibt der US-amerikanische Präsident die Friedensbemühungen maßgeblich voran, andererseits werden von US-amerikanischer Seite mutmaßlich die Waffenlieferungen fortgesetzt und Starlink nicht abgeschaltet, was erheblich zum abrupten Beenden des sinnlosen Sterbens beitragen würde.
Verträge sind zu erfüllen? Sicherung der US-amerikanischen Interessen? Druckmittel auf Russland? Und Europa? Europa, vor allem Deutschland, Frankreich und Großbritannien geben weiterhin den Geisterfahrer und haben immer noch nicht mitbekommen, dass sie in der Beilegung des Ukraine-Kriegs nicht das geringste zu sagen haben. Sie spielen sich aber auf, als hätten sie und machen „einen auf dicke Hose“. Murmeln werden als Eier verkauft.
Etwas aus dem Fokus der Neuen Medien gerät dabei der immer noch wütende Krieg im Gaza-Streifen mit einer israelischen Planier-Raupe, dessen Vorgeschichte noch länger ist, als die, die zum Ukraine-Krieg geführt hat. Rund 80 Jahre, aber auch hier eigentlich noch länger. Man kann sich vorstellen, wie lange es hier dauern wird, bis sich sichere, friedliche Verhältnisse einstellen können.
Wer kann sicher sein, wer nimmt sich das Recht heraus zu behaupten, wer entscheidet darüber, dass sich Zustände, wie im 3. Reich, die Verfolgung und Vernichtung einer Minderheit, damals die Juden, nicht wiederholen kann? Seitdem das geschehen ist, hat sich der Großteil der Menschheit keinen Millimeter weiterentwickelt.
Wenn gerade Deutsche Anzeichen für eine Wiederholung dieser tief-dunklen Zeit zu erkennen glauben, derzeit in dem, wie der israelische Staat mit dem Gaza-Streifen verfährt, dann ist das keine Verharmlosung der Gräueltaten im 3. Reich, sondern der Beweis dafür, dass es doch einige gibt, die aus der Geschichte gelernt haben, und die der Meinung sind, dass sich so etwas niemals mehr wiederholen darf.
Um auf einen Genozid hinzuweisen, muss jeder Vergleich möglich und erlaubt sein. Es geht um eine Mehrzahl von Menschen, von Familien, die einfach nur in Frieden leben wollen! Ungeachtet der Tatsache, dass es auf beiden Seiten Kräfte gibt, die das nicht interessiert.
Besonders tragisch wird es, wenn dieser Genozid augenscheinlich ausgerechnet von denen ausgeht, die selbst so schrecklich davon betroffen waren.
Wie kann sich der deutsche Staat erdreisten, diejenigen als Anti-Semiten zu bezeichnen, die hier Merkmale eines Genozids zu erkennen glauben und versuchen, diese kritischen Stimmen zu unterdrücken, „nur“, weil es sich um den Staat Israel handelt, der hier als Täter infrage kommt. Auch der Staat Israel hat keinen Freibrief, die Bevölkerung im Gaza-Streifen nach seinen Vorstellungen und Überzeugungen abzurasieren.
Ein Genozid ist ein Genozid, egal von welcher Regierung eines Landes er begangen wird.
Der Staat Israel ist keine Ausnahme! Im Gegenteil. Aufgrund der Erfahrung seines Volkes müsste es die Menschlichkeit gebieten, dass derartiger Völkermord nie wieder geschieht.
Weiter müsste der Begriff Anti-Semitismus einmal genau unter die Lupe genommen werden, was wer aus welchen Gründen darunter versteht. Man kann den Eindruck gewinnen, dass dieser Begriff vor allem als Totschlagargument verwendet wird, um kritische Stimmen mundtot zu machen. Besonders bei diesem heiklen Thema wäre absolute Akkuratesse dringend notwendig.
Es ist die Pflicht eines jeden, der Kritik an den Zuständen üben will, nicht zu verallgemeinern.
Nicht alle israelischen Staatsbürger sind Netanjahu-Anhänger (das zeigen die Demonstrationen), nicht alle Juden sind Zionisten, nicht einmal alle Zionisten sind Juden.
Und sicher sind auf der Gaza-Seite ebenfalls nicht nur „Engel“ unterwegs!
Beide Lager haben rund 80 Jahre Zeit gehabt, den gegenseitigen Hass durch gegenseitige Provokationen aufzubauen und ihn immer wieder sich entladen zu lassen.
Dieser unermessliche Hass kann nur über Generationen hinweg wieder abgebaut werden.
Wenn es jemals eine ernste Absicht gegeben hätte, eine 2-Staaten-Lösung zu realisieren, wäre diese schon längst in die Tat umgesetzt worden. Wenn jedoch der politische Wille dazu fehlt, vor allem auf der Seite des Stärkeren, passiert gar nichts. Und der fehlt jetzt schon seit rund 80 Jahren.
Maßgeblich durch die Briten ist der Staat Israel künstlich entstanden. Die Ableitung der Nutznießer auf einen Gebietsanspruch aus einem Glauben heraus, ist einmalig.
In dem nicht natürlich entstandenen, sondern künstlich geschaffenen Staatsgebilde liegt möglicherweise die Wurzel allen Übels, die von langer Hand, spätestens durch die Balfour-Deklaration im Jahre 1917 ihren Anfang genommen hat.
Man hat nun Jahrzehnte lang Zeit gehabt, zu beobachten, dass dieses Konstrukt ein sicheres Leben und eine Garantie für friedliche Verhältnisse aller nicht zustande gebracht hat. Schmerzliche Erfahrungen auf beiden Seiten haben bislang nicht dazu geführt, dass man zu der Einsicht gekommen wäre, dass man sich möglicherweise auf dem Holzweg befindet.
Die verfeindeten Lager müssten sich, neutral moderiert (welcher Staat, welcher Mensch ist heute noch neutral, oder zumindest kein Interessenvertreter?), zusammensetzen und sich in sicher nicht einfachen, langwierigen, zähen Gesprächen und Verhandlungen über die Neugründung eines gemeinsamen Staates für alle Beteiligten ernsthaft nachdenken, solange, bis es zu einer Einigung gekommen wäre, die für alle Beteiligten akzeptabel ist. Das Ergebnis, eine gemeinsame Staatenlösung, müsste das erklärte Ziel sein und wenn es noch so lange dauern würde.
Das Mitspracherecht müsste nach Bevölkerungsanteil in einem gerechten Verhältnis festgelegt werden. So müssten kleinere Anteile verhältnismäßig mehr Stimmanteile haben, als der größere Anteil, um zu möglichst für alle gerechten Entscheidungen zu gelangen, die alle Beteiligten mittragen könnten. Ein Vorankommen wäre nur durch Vernunft, nicht durch Starrsinn möglich.
Aufgrund der hitzigen Mentalität aller Beteiligten müssten beide Lager auf Gedeih und Verderb voneinander abhängig gemacht werden, sodass ein friedliches Zusammenraufen immer wieder nötig wäre, weil niemand in der Lage wäre, die Oberhand zu gewinnen.
Es müssten gegenseitige Abhängigkeiten geschaffen werden. So könnten zum Beispiel Lieferungen von Lebensmitteln, Wasser, Energie (Israel) usw. mit der Hoheit über die noch zu erschließenden Gasfelder (Gaza) vor Gaza „verrechnet“ werden, ohne, dass die USA oder sonst wer die Finger im Spiel haben.
Bei derartigen gegenseitigen Abhängigkeiten würde man sich schon zusammenraufen.
Das alles setzt voraus, dass der Mensch an sich seine menschlichen Schwächen unter Kontrolle bringen würde. Hierzu können Machtstreben, Geldgier, Rechthaberei, Überheblichkeit, Ideologien, Ansprüche aus einem Glauben heraus usw. gezählt werden.
Jerusalem müsste einen Sonderstatus erhalten und die Verwaltung müsste unter den drei Weltreligionen aufgeteilt werden. Jerusalem könnte im „Kleinen“ ein Beispiel dafür sein, wie der gesamte neue Staat im „Großen“ funktioniert. Und möglicherweise würde er so in der Tat funktionieren.
Für viele mag das alles vielleicht naiv oder sogar absurd klingen. Zur Herstellung von Frieden, Frieden in dem jede Mutter, gleich welcher Religion sie angehört, ihre Kinder in Sicherheit aufwachsen sehen kann, muss jede Überlegung und Idee, wie ein friedliches Miteinander realisiert werden kann, erlaubt sein zu denken und auch auszusprechen.
Eines ist sicher. So, wie die Verhältnisse in der Vergangenheit gestaltet wurden, hat die Realität eindeutig gezeigt, dass es so auf gar keinen Fall funktioniert. Also, warum nicht einfach einmal das Gehirn durchblasen, alte, überkommene Überzeugungen loswerden und endlich einmal etwas Neues denken?
Und wer jetzt immer noch sagt, das wäre eine Delegitimierung des Staates Israel, der sollte seine Gehirnwindungen einmal zur Inspektion bringen. Der Mensch, egal welcher Couleur und welcher Religion steht hier im Mittelpunkt. Im Mittelpunkt stehen Überlegungen, wie ein friedliches Miteinander möglich sein könnte. Falls sich herausstellt, dass das eine Utopie ist, auch gut, aber immerhin sind sich Gedanken gemacht worden, die von den eingefahrenen, zu nichts außer Elend führenden Entscheidungen abweichen. Und wenn es nur zur Anregung für andere Ideen dient, dann wäre schon viel getan. Und das ist weder anti-semitisch, noch anti-israelisch, noch anti-christlich, noch anti-moslemisch, noch anti-sonst wie, sondern vor allem ein Appell an die Vernunft, zu der der Mensch schließlich auch begabt ist.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von Georg Ohrweh)
-
 @ c9badfea:610f861a
2025-05-12 16:29:32
@ c9badfea:610f861a
2025-05-12 16:29:32- Install Organic Maps
- Launch the app and download the World Map first
- Tap the ☰ at the bottom, then select Download Maps, and tap the + icon
- Download maps by tapping ⤓ next to your desired region
- Return to the main screen and tap 🔍 to search for your destination
- Enjoy navigating offline
ℹ️ Note that Organic Maps does not provide live traffic updates
-
 @ 6be5cc06:5259daf0
2025-05-12 14:50:36
@ 6be5cc06:5259daf0
2025-05-12 14:50:36A posição do libertário que rejeita o cristianismo padece de sérias incoerências lógicas, históricas e filosóficas. Ao renegar as bases espirituais e culturais que tornaram possível o próprio ideal libertário, tal posição demonstra ser, ao mesmo tempo, autofágica e irracional. É o caso de alguém que se gloria dos frutos de uma árvore que corta pela raiz.
I. Fundamento histórico: a civilização da liberdade é cristã
Não foi o secularismo moderno, nem o paganismo antigo, que ergueram as instituições que protegem a dignidade da pessoa humana e os limites ao poder. Desde os primeiros séculos, a Igreja resistiu ao culto estatal romano, afirmando a soberania de Deus sobre os Césares — "Mais importa obedecer a Deus que aos homens" (Atos 5,29).
Foi o cristianismo que:
-
Fundou universidades livres, onde o saber era buscado sob o primado da verdade;
-
Defendeu a lei natural como fundamento do direito — uma doutrina que protege o indivíduo contra tiranias;
-
Resgatou e aprofundou o conceito de pessoa, dotada de razão e livre-arbítrio, imagem de Deus, e, portanto, inalienavelmente digna e responsável.
Em momentos-chave da história, como nas disputas entre papado e império, nas resistências contra absolutismos, e na fundação do direito internacional por Francisco de Vitoria e a Escola de Salamanca, foi o cristianismo quem freou o poder estatal em nome de princípios superiores. A tradição cristã foi frequentemente o principal obstáculo à tirania, não seu aliado.
Negar isso é amputar a própria genealogia da liberdade ocidental.
Uma das chaves do cristianismo para a construção dessa civilização da liberdade foi a exaltação do individualismo. Ao afirmar que o ser humano é feito à imagem de Deus e que sua salvação é uma escolha pessoal, o cristianismo colocou o indivíduo no centro da moralidade e da liberdade. Diferente dos gregos, cuja ética era voltada para a polis e a cidade-estado, o cristianismo reafirma a suprema importância do indivíduo, com sua capacidade de escolha moral, responsabilidade pessoal e dignidade intrínseca. Esse princípio, mais do que qualquer outra religião, foi o alicerce do desenvolvimento da liberdade individual e da autonomia, valores que sustentam a civilização ocidental.
A ética grega, na melhor das hipóteses, descreve a ordem natural — mas não consegue justificar por que essa ordem deveria obrigar a vontade humana. Um Logos impessoal não tem autoridade moral. Uma ordem cósmica sem um Legislador é apenas um dado de fato, não uma norma vinculante. A vontade pode rebelar-se contra o telos — e sem um Deus justo, que ordena a natureza à perfeição, não há razão última para não o fazer.
A cultura grega teve uma influência indiscutível sobre o desenvolvimento da civilização ocidental, mas o cristianismo não só absorveu o que havia de bom na cultura grega, como também elevou e completou esses aspectos. O cristianismo, ao afirmar que todos os homens são feitos à imagem e semelhança de Deus e têm dignidade intrínseca, levou a uma noção de igualdade moral e liberdade que transcende as limitações da pólis grega.
II. Falsa dicotomia: fé e liberdade não são opostas
Com frequência equiparam a religião à coerção e à obediência cega. Mas isso é um equívoco: o cristianismo não se impõe pela força, mas apela à consciência. O próprio Deus, em sua relação com a criatura racional, respeita sua liberdade. Como ensina a Escritura:
"Se alguém quiser vir após mim..." (Mt 16,24);
"Eis que estou à porta e bato. Se alguém ouvir a minha voz e abrir a porta, entrarei em sua casa e cearei com ele." (Ap 3,20);
"Assim falai, e assim procedei, como devendo ser julgados pela lei da liberdade." (Tiago 2,12).A adesão à fé deve ser livre, voluntária e racional, pois sem liberdade não há verdadeiro mérito, nem amor genuíno. Isso é mais compatível com o princípio de não agressão do que qualquer utopia secular. Ora, o núcleo do evangelho é voluntarista: salvação pessoal, conversão interior, caridade.
Ninguém deve ser forçado, contra sua vontade, a abraçar a fé, pois o ato de fé é por sua natureza voluntário (Dignitatis Humanae; CDC, cân. 748,2)
Se algum Estado usa da força para impor o cristianismo, afirmar que o cristianismo causou as coerções é tão equivocado quanto dizer que a propriedade privada causa o comunismo; é uma inversão da realidade, pois o comunismo surge precisamente da violação da propriedade. Portanto, a fé forçada é inválida em si mesma, pois viola a natureza do ato de crer, que deve ser livre.
III. Fundamento moral: sem transcendência, o libertarianismo flutua no vácuo
O libertário anticristão busca defender princípios objetivos — como a inviolabilidade do indivíduo e a ilegitimidade da agressão — sem um fundamento transcendente que lhes dê validade universal. Por que a agressão é errada? Por que alguém tem direito à vida, à liberdade, à propriedade? Sem uma explicação transcendental, as respostas para tais perguntas se tornam apenas opiniões ou convenções, não obrigações morais vinculantes. Se a moralidade é puramente humana, então os direitos podem ser modificados ou ignorados conforme a vontade da sociedade. O conceito de direitos naturais, tão caro ao libertarianismo, precisa de um solo metafísico que justifique sua universalidade e imutabilidade. Caso contrário, eles podem ser tratados apenas como acordos utilitários temporários ou preferências culturais, sem qualquer obrigatoriedade para todos os seres humanos em todas as circunstâncias.
Pensadores libertários seculares, como Ayn Rand e Murray Rothbard, tentaram ancorar os direitos naturais na razão humana ou na natureza do homem. Rand baseia sua ética no egoísmo racional, enquanto Rothbard apela à lei natural. Embora essas abordagens busquem objetividade, elas carecem de uma resposta definitiva para por que a razão ou a natureza humana obrigam moralmente todos os indivíduos. Sem um fundamento transcendente, suas concepções permanecem vulneráveis a interpretações subjetivas ou a cálculos utilitários.
Aqui, o cristianismo oferece uma explicação sólida e transcendental que fundamenta os direitos naturais. A visão cristã de que o ser humano foi criado à imagem e semelhança de Deus confere à pessoa uma dignidade intrínseca, imutável e universal. Essa dignidade não depende de fatores externos, como consenso social ou poder político, mas é uma característica inerente ao ser humano pela sua criação divina. A partir dessa perspectiva teológica, torna-se possível afirmar com base sólida que os direitos naturais são dados por Deus e, portanto, são universais e vinculantes.
O cristianismo também é a base de um sistema moral que distingue claramente justiça de legalidade. O Estado pode criar leis, mas isso não significa que essas leis sejam justas. A justiça, sob a ótica cristã, é uma expressão da ordem moral objetiva, algo que transcende as leis humanas e é definido pela vontade divina. Por isso, o libertarianismo cristão vê a agressão como uma violação de uma ordem moral objetiva, e não apenas uma violação de uma convenção social ou de um acordo utilitário.
Se a moralidade e os direitos naturais não forem fundamentados em um Logos criador e legislador, o que acontece é que o conceito de direito natural degenera para algo mais frágil, como um simples acordo utilitário. Nesse cenário, os direitos do indivíduo se tornam algo acordado entre os membros de uma sociedade, em vez de princípios imutáveis e universais. Os direitos podem ser negociados, alterados ou ignorados conforme o interesse do momento.
IV. Fundamento científico: a racionalidade moderna é filha da fé cristã
A ciência moderna só foi possível no contexto cultural cristão. Nenhuma outra civilização — nem a grega, nem a islâmica, nem a chinesa — produziu o método científico como o Ocidente cristão o fez.
Isso se deve a quatro premissas teológicas:
-
Criação racional: O mundo é ordenado por um Deus racional.
-
Distinção entre Criador e criatura: A natureza não é divina e pode ser estudada sem sacrilégio.
-
Valor do trabalho e da observação empírica, herdado do monaquismo.
-
Autonomia institucional, presente nas universidades medievais.
A doutrina cristã da Criação ex nihilo ensina que o mundo foi criado por um Deus racional, sábio e pessoal. Portanto, o cosmos é ordenado, possui leis, e pode ser compreendido pela razão humana — que é imagem do Criador. Isso contrasta fortemente com as cosmovisões panteístas ou mitológicas, onde o mundo é cíclico, arbitrário ou habitado por forças caprichosas.
Sem essa fé no Logos criador, não há razão para crer que a natureza tenha uma ordem inteligível universal e constante, que pode ser descoberta por observação e dedução. A ciência moderna só é possível porque, antes de investigar a natureza, pressupôs-se que ela era investigável — e isso foi uma herança direta do pensamento cristão.
Homens como Bacon, Newton, Kepler e Galileu viam na ciência um modo de glorificar o Criador. O ateísmo cientificista é, portanto, parasitário da teologia cristã, pois toma seus frutos e rejeita suas raízes. A ciência moderna nasceu como filha legítima da fé cristã. E os que hoje a usam contra sua mãe, ou são ingratos, ou ignorantes.
V. O cristianismo como barreira à revolução cultural
O cristianismo é a barreira mais sólida contra a infiltração revolucionária. A chamada "marcha gramsciana", que visa corroer os fundamentos morais da sociedade para subjugar o indivíduo ao coletivo, encontra sua resistência mais firme nos princípios cristãos. A fé cristã, ao proclamar a existência de uma verdade objetiva, de uma lei moral imutável e de uma dignidade humana que transcende o Estado e o consenso social, imuniza a civilização contra o relativismo e o igualitarismo nivelador do marxismo cultural.
Além disso, o cristianismo é uma tradição milenar, profundamente enraizada no cotidiano das pessoas, não sendo uma novidade a ser imposta ou implementada, mas uma força presente há séculos, que permeia a estrutura social, moral e cultural da sociedade. Sua presença constante nas comunidades, desde os tempos mais antigos, oferece uma resistência robusta contra qualquer tentativa de subverter a ordem natural e moral estabelecida.
Não por acaso, tanto Karl Marx quanto Antonio Gramsci identificaram no cristianismo o principal obstáculo à realização de seus projetos revolucionários. Marx chamou a religião de "ópio do povo" porque sabia que uma alma ancorada em Deus não se submete facilmente ao poder terreno; Gramsci, mais sutil, propôs a destruição da cultura cristã como pré-condição para o triunfo do socialismo. Sem essa âncora transcendente, a sociedade torna-se presa fácil das engenharias sociais que pretendem redefinir arbitrariamente o homem, a família e a liberdade.
Conclusão
O libertário anticristão, consciente ou não, nega as fundações mesmas do edifício que habita. Ao rejeitar o cristianismo, cava o abismo sob os próprios pés, privando o ideal libertário de sua base moral, cultural e racional. Ele defende a ética voluntária, a liberdade individual e a ordem espontânea, mas sem o solo metafísico e histórico que torna esses princípios inteligíveis e possíveis. É um erro tentar preservar a liberdade em termos absolutos sem reconhecer as raízes cristãs que a sustentam, pois o cristianismo é a única tradição que a legitima e a viabiliza.
Negar o cristianismo é racionalmente insustentável. A liberdade, como a conhecemos, é filha da fé cristã, que oferece a base moral e metafísica que torna a liberdade tanto desejável quanto possível. Mesmo que ateu, o libertário que ama a liberdade deveria, no mínimo, respeitar — e, idealmente, redescobrir — essas raízes cristãs. Pois sem fé, restam apenas o niilismo e o relativismo, que, eventualmente, desaguam na servidão.
Como nos ensina a tradição: Ubi fides ibi libertas — onde há fé, há liberdade.
-
-
 @ eabee230:17fc7576
2025-05-12 14:38:11
@ eabee230:17fc7576
2025-05-12 14:38:11⚖️ຢ່າລືມສິ່ງທີ່ເຄີຍເກີດຂຶ້ນ ຮອດຊ່ວງທີ່ມີການປ່ຽນແປງລະບົບການເງິນຈາກລະບົບເງິນເກົ່າ ສູ່ລະບົບເງິນໃໝ່ມັນເຮັດໃຫ້ຄົນທີ່ລວຍກາຍເປັນຄົນທຸກໄດ້ເລີຍ ນ້ຳພັກນ້ຳແຮງທີ່ສະສົມມາດ້ວຍຄວາມເມື່ອຍແຕ່ບໍ່ສາມາດແລກເປັນເງິນລະບົບໃໝ່ໄດ້ທັງໝົດ ຖືກຈຳກັດຈຳນວນທີ່ກົດໝາຍວາງອອກມາໃຫ້ແລກ ເງິນທີ່ເຫຼືອນັ້ນປຽບຄືດັ່ງເສດເຈ້ຍ ເພາະມັນບໍ່ມີຢູ່ໃສຮັບອີກຕໍ່ໄປເພາະກົດໝາຍຈະນຳໃຊ້ສະກຸນໃໝ່ ປະຫວັດສາດເຮົາມີໃຫ້ເຫັນວ່າ ແລະ ເຄີຍຜ່ານມາແລ້ວຢ່າໃຫ້ຄົນລຸ້ນເຮົາຊຳ້ຮອຍເກົ່າ.
🕰️ຄົນທີ່ມີຄວາມຮູ້ ຫຼື ໃກ້ຊິດກັບແຫຼ່ງຂໍ້ມູນຂ່າວສານກໍຈະປ່ຽນເງິນທີ່ມີຢູ່ເປັນສິນສັບບໍ່ວ່າຈະເປັນທີ່ດິນ ແລະ ທອງຄຳທີ່ສາມາດຮັກສາມູນລະຄ່າໄດ້ເຮັດໃຫ້ເຂົາຍັງຮັກສາຄວາມມັ້ງຄັ້ງໃນລະບົບໃໝ່ໄດ້.
🕰️ໃຜທີ່ຕ້ອງການຈະຍ້າຍປະເທດກໍ່ຈະໃຊ້ສິ່ງທີ່ເປັນຊື່ກາງໃນການແລກປ່ຽນເປັນທີ່ຍ້ອມຮັບຫຼາຍນັ້ນກໍຄືທອງຄຳ ປ່ຽນຈາກເງິນລະບົບເກົ່າເປັນທອງຄຳເພື່ອທີ່ສາມາດປ່ຽນທອງຄຳເປັນສະກຸນເງິນທ້ອງຖິ່ນຢູ່ປະເທດປາຍທາງໄດ້.
🕰️ຈາກຜູ້ດີເມື່ອກ່ອນກາຍເປັນຄົນທຳມະດາຍ້ອນສັບສິນທີ່ມີ ບໍ່ສາມາດສົ່ງຕໍ່ສູ່ລູກຫຼານໄດ້. ການເກັບອອມເປັນສິ່ງທີ່ດີ ແຕ່ຖ້າໃຫ້ດີຕ້ອງເກັບອອມໃຫ້ຖືກບ່ອນ ຄົນທີ່ຮູ້ທັນປ່ຽນເງິນທີ່ມີຈາກລະບົບເກົ່າໄປສູ່ທອງຄຳ ເພາະທອງຄຳມັນເປັນສາກົນ.
ໃຜທີ່ເຂົ້າໃຈ ແລະ ມອງການໄກກວ່າກໍ່ສາມາດຮັກສາສິນສັບສູ່ລູກຫຼານໄດ້ ເກັບເຈ້ຍໃນປະລິມານທີ່ພໍໃຊ້ຈ່າຍ ປ່ຽນເຈ້ຍໃຫ້ເປັນສິ່ງທີ່ຮັກສາມູນລະຄ່າໄດ້ແທ້ຈິງ.🕰️ເຮົາໂຊກດີທີ່ເຄີຍມີບົດຮຽນມາແລ້ວ ເກີດຂຶ້ນຈິງໃນປະເທດເຮົາບໍ່ໄດ້ຢາກໃຫ້ທັງໝົດແຕ່ຢາກໃຫ້ສຶກສາ ແລະ ຕັ້ງຄຳຖາມວ່າທີ່ຜ່ານມາມັນເປັນແບບນີ້ແທ້ບໍ່ ເງິນທີ່ລັດຄວາມຄຸມ ເງິນປະລິມານບໍ່ຈຳກັດ ການໃຊ້ກົດໝາຍແບບບັງຄັບ. ຖ້າຄອບຄົວຫຼືຄົນໃກ້ໂຕທີ່ຍູ່ໃນຊ່ວງເຫດການນັ້ນແຕ່ຕັດສິນໃຈຜິດພາດທີ່ບໍ່ປ່ຽນເຈ້ຍເປັນສິນສັບ. ນີ້ແມ່ນໂອກາດທີ່ຈະແກ້ໄຂຂໍ້ຜິດພາດນັ້ນໂດຍຫັນມາສຶກສາເງິນແທ້ຈິງແລ້ວແມ່ນຍັງກັນແທ້ ເວລາມີຄ່າສຶກສາບິດຄອຍ.

fiatcurrency #bitcoin #gold #history #paymentsolutions #laokip #laostr
-
 @ 4bc7982c:4cb5c39d
2025-05-12 14:21:38
@ 4bc7982c:4cb5c39d
2025-05-12 14:21:38-----BEGIN PGP PUBLIC KEY BLOCK----- mQINBFav2jMBEADPCRsFp9Vtw0vlkeho2v8lIPblVNNeW43HLNXeEGvgn+gaK5sW 9H5mbp6ZLEjbdEr7zc3eu7iLFudw9IdJCLKYcqkXWBpAQF7JF6l4J18oOQK1Tfzc QyU5jWuAcc+Ds8REW91X/N9Ae/QF+dtRyuv1ILFKZ88G2za/TdV06PuNdyi3qTlD 5HPVhd5YrZyY7GVG1gTi7Wtj6tONGjjQARR6T1LDuN75QmoDvw3m68U5QnoECGg4 BFAdPrnFxYpTCl6SyV9AsCfzTwP2mIkLKZi7X/wSubt4b+nhPMuFeZ/6XFCfHCD4 mEcQudyXByi7FgAXmX+UPS1iFtaXG8UJHM4Fq2k5FcjdLXW2s0kKk915XVEE9Q4Y wWQpTonr9FwgT+aSbV7UX8ihNhNCSQAv1RnIIt8t9hncztfZD7g/FMj4FfZ8GkI0 gmn3DliSlswBZbr1rN0HTitAzYKNUsiinIxwICfj9yRTcQ92F0ML+zwQB5UOXjEJ ra+D3tGjyVCNKO940rbjvj/QAvakoNBdCnbaZDKf26Hc0qpcn3DvGei0QLFJ2gmz EnK1dW4kftcJE8piibvq35EEptqkDiCMlI0Eq819vtJBumF3ZSBjMeEB1IPfSvDG 1OoUXXS0TGwCGstjMTRQ1S2D8fDb0ENBrbdhyWXZVQFzxi/YMwkNGswDoQARAQAB tBpzaGlub2hhaSA8YnRjaW5mb0BzZGYub3JnPokCNwQTAQgAIQIbAwIeAQIXgAUC Y+g7QQYLCQgHAwIGFQgCCQoLAxYCAQAKCRBKdYg8wbHTTG6OD/wJ9V3tjvaerA6Y GViWU6h0Nrvjs6/NWq48K3hP9eqy9n7CKVOviCjglF/yf1FEfEDg7LKYtFYLs1pf MFzNolynfGearK7HQeOXRoNFfkDqQWcjPWeVWhkEgxrqq9AMg+7gHMMtKnHWezJT E4NaAui7uW7rTiOvS8PT8+Y3uATermzJ0Cmb1c0su/s9in3bPwnmxJpbj9EruOWg MVY8Hov5fEJTwghIwoVBR2D4nWObQMWQsiNrEG/XdPeE1XzHGLrSmH64o6T2vWK2 XkQU6TVDBKhsIy0EjX9B36Hx+MmFx1pfHfxtGpAgZKwnEnMIoNc2vvrkjJhnRCUQ 1MfMoPDnn01mOT/kNkijyTUlh4rYeqa/A5JuqLbQ6qWz4e9rodu9C6/drn7Ivk/D ipRyMihNKbWq1PkAr7I9YQ/1NAM8ZmUE/bFL7/t6rDsa5IinwUeu/WGqNmKHIo0o u5vQD9zwmYOqeZLo2vzmmr/NkaRD7/3j5pb81MTjZzqTh/BGI31TEbjWpJ4StJ4g 2QNcXamGa/7/TpgI5u2EQojdvUojzSg7V3/ZNsNaJnDnqtZNzY7n2q4qvE2H/xJq z5y0SsTgpMPktt+ljg/T3po/LGQIcCPE4EBpSBKSpi0VWvkGVM2sraUCzP82c/X+ ztr12YwcckdET9SWDtSloE942tXKO4kCOQQTAQgAIwUCVq/aMwIbAwcLCQgHAwIB BhUIAgkKCwQWAgMBAh4BAheAAAoJEEp1iDzBsdNMrLMP/1pQZUXNzG9FlhBBGA8X ko+ObEvuVUvtZzTu8DXrQGDp/DYQq+O7YWhZ8WwyxYJx718bkIemHP5IbXbzmeS3 Nijf1mszrCbmw7QZ496YTihoZxyeb8MHYECPAiUbz9Ie2S6/isF45LZX3SbkwlYc M5UfV4iaXqvKSuydRJ8Xk68rn+AiEXFrv1vcGy7cqDz4PBOd9ZJwiAWhr0m9hMZT uDqYPI8choUh3uhpMIEf9YLD77ru1xl0Uba8e34qrOs+Secfv81ItbFION9z0A17 W2/q01dQfojpcoC+YS3CXXCJGm5TwYniIWVUmtL4eIfg6T/ZX5o5Am3aj4pQxr+E y/NNkUvplXZ+nG3fG4mthY4r+NV4E/RSsZJDU55BAWhZj3fHVhu7Q40yVMHLJNP9 KKCdacd/WWJtUX3Z1X/mQplJcMCYwhvdPNCctDpHrEyuIlvDvJuqbCY5eBa0hk8z jRNA9IghWW7JMzcnQR5u6FXWiqmcfFOEJwDUu8hM057Q6e6/FRPjlmua6SzcMK+k ERS+AwAIX4BIaLCnE7ndizQ/y6ek2hpKFXzPBLmxLyID91/wlA6NzbtyZkgZvJ7X g/7Rtt4FyZwKZqbfBFrjzLIyFTkmJ0lSPCSuWna5vaSg1HXPfc05wOUXsGV8xA8D zrolAoj4OIo//H2YMvLy5Giz0f8AACeO/wAAJ4kBEAABAQAAAAAAAAAAAAAAAP/Y /+AAEEpGSUYAAQEAAAAAAAAA/9sAQwAIBgYHBgUIBwcHCQkICgwUDQwLCwwZEhMP FB0aHx4dGhwcICQuJyAiLCMcHCg3KSwwMTQ0NB8nOT04MjwuMzQy/9sAQwEJCQkM CwwYDQ0YMiEcITIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIy MjIyMjIyMjIyMjIy/8AAEQgAyADIAwEiAAIRAQMRAf/EABwAAAIDAQEBAQAAAAAA AAAAAAYHAAQFAwIIAf/EAEkQAAEDAwIDBAcFAwgIBwAAAAECAwQABREGEgchMRNB kaEUIjJRcYGxFSNCYcEIUtEWFyQlM1OSohg0YmNzgpPSQ1RVcpTC4f/EABkBAAMB AQEAAAAAAAAAAAAAAAABAgMEBf/EACIRAAICAgIDAQEBAQAAAAAAAAABAhEDEiFB EzFRBCJhgf/aAAwDAQACEQMRAD8AAbvwd1NZkuKf9GWhH4miog/5aEpOn50UkLQC R7s/rX0K1xpmuEJk6RW4g9exloX5GuMvibpeY2U3TRFxCVclH0dKh4irpfBWfOog P4yUgVyMdwHG2n8q8cGZQw/CfiLV3dk4nH58q/E2Pg/NwpjUaWCT0W4QfMUUgEN6 C9tzgAfnX43DdcHq4p/p4XaLnpzA1iypJ6BTqD+teU8CkryYd/jOJ7iBn6UUg5EM LbII9kVbg6emTpAZSppsnvcJApxyOBd/59nNiLx05kVjyeEesYSj2cL0gD+6dHOi ogZ8DgVqO4xw8zcbVgjOC8rPkmhu8cO7zZXFokKZVsOCUbv1FFyLBru0glqLdI5/ 2Mn6VbTf+IEMhMiRJUnG3ZIjBWfmRRURWxPrirQspJTkcq/RDdV0xTYe1Jc3QW7h YLPKHeVxSlXiDWQ87ZXlZd0p2ZByr0WUpvPjmqSiDbMDTWg7nqdakxZENnb3vubc +Ao1T+zvqpYym4Wkj3h1f/bWIpzTvLbbb3BXn2mZKXCPHFbdvviIiQImr79EGOQe ZCgPjg0nFdMSk+z9/wBHXVf/AKhaf+ov/tqf6Ouq/wDz9p/6q/8Atrft2v782/ln XMGU2kY7OdAUgH/mAzW9B4lanW+cq01NQPwNSy2o+NTqyrFPO4Oaht7qm3JEFRBx lKl8/wDLVNPC29KyPSYQI961fwp9t6/vTqgqToztmu9Uae04fkDiuL2tbSFf0/Q1 8ZCj6znogUB80mjVlKhDq4ZXhPWTC/xq/hVJ/Qs+ODvlw+XuUr+FPh3UfDt93Y8u 4QlH+9YWgDxFeC3w5lqAZ1THCjyw4sfrRqPg+endOyWjjtmD+YJ/hXH7Ekf3jXia +j/5C6amDETUNvcUroN6D+tVX+D6lt5iy4iyf3TVJR7Jkn0Ii26Rm3KSlhuRFbUr oXVkD6Uao4CamcY7VE+1KTt3eq8o/wD1oqk8HryzktJS57tjnOqY0jra0J+4Vcmw ByKCVAU6gZtyFvdNAXa0qUl9xhRT12bv1FSmC7c9dQhskPreQOqZEYHPzxUqtYBc hTtKlME7FOIPfg4q43ebnGQezlvpJ9yzX0C3qrhFfiS8iEy4eoejls/TFezw/wCG moGyqDMaST0LEkcvkaj0aUINrUl1BClvhwjudbSr9KujUvapPptmtkjPXDZQfKnH J4B2p5sGDeHkH3qbCgfCh2ZwEvUcqMSdGkp7gfUNPZCoXyZumHkff2F1pZ6lh7p8 M1aaNkSE+gX26wFk9FlRCfA1rT+Eeq4gUr7OLgH90QrND0jSN9hubH7dJQT72zTt DQSQp2qY53WniAh0p9lt50pz/izW7D1lxVgrKu1hXJHuOwj5EEUrXYLrR2rScjuK ajfpjQ+7cWgZ/CsilaHSHQ1xo1Tb1BF20gVH8RacI/Q1qxOPWnpDgbn2qbG7iVIC wKSsW/32IrLdwlJ/LfkedXV6wmrAEuJCkj8RcjgE/MU6iNJD0b4gcNLsrD0uElau X37JSfpV1myaBvCCYbkFee9h8Z+tfPxv9ikIKZOnGUk/iYcKT51G2NHvthYfuNue V1ASFpHzHOp1XQOI/JHCyyyMqjvLQD05BQrIkcH0bVFmSws9yVNkedLCEJUcZsev XAB7KHXFtjwPKiOFqbiVCSFsTY9zR0GVIXn4YOaWrJ1NWRwkmZ5R2T+bazWa7w3m RchcV/HvCc1bb4u6yty9l20yhZ7i2FDNacXj/ZgsN3O0Toa+8gpWKlwbGkD8TSzl tkJc7HtOfNDoIzTLtsOxPxWk9q/EexzDT6gM/PlVeJxU0NdkpC57aNwyBIaKa2oz +lryN8OVDd/4TgBHyqanH0Pj4fjmnS+3hi7OLQR7LzaHUnyofuOhj2brztrs8wJS TybUyo+HKi9uysJAUw+4kdxCs1+O2l9aFIEtSkqGCFE01kl2SJF3T+m5MdyQ7ZJ8 FaTgvRF9okfOqH2NBSlRt+sZcRwD1Q+laPMGm1O0YVRlMI7TslHJS2vA8KE7joV3 CkbnkoHetGRTWV9oaBuIeIkUA2nV7E9tPQGQlXyIUK2GNc8U7V61wsUe4N95bTt8 01hSNBPtKKmZSASe7Kaz1QdVWlRMSfJCEnklt448KayRfspJBwzxtW24W73pKQxj qpCgryIqUEHV2qYQxMaTJSe6QylVSrTgS0gPTcdJSifSbDJYUe+NI5eBqzHiaSc3 GPerhbz/AL9rI8RXiZw91RbiRJsspPLOQncPKsR61SWSQ/FeQR3LQRVbDDCDDuzL gcsevGlbT6qTKUg+BokjX/i3bAC1KbuKCeXrodz4EHFKURdp9nmPfXdrtmFb2XHW le9Cyk+VCkuxUN1rjVre2L23XTbS0jkT2S2/MZFbET9oO2LA+1LFJZ7tyCFjzpOx tU6ggoKGbtKCP3VnePOryddT3AlM6DbZqU9zsYDPzFH8MKHVG4m8NL/lEtpppajj EmKAfEVcTYOGV/GIjsEKHXsXtp86Rwv2mLgpX2npdltSvxRHijFeVQdCSQOyk3SA 4T1JStIH1o0j0w5Ha9wcsEpBXBuDwz09ZKh5VhTOB0oEmNcGFjuCwU0vIlljtrSq x6/bjlPMB9xbWfh3URx5fFC2JSYOoGrkjPIIfQ/kfDrih430w5Okvg9fWNxTDQ8B 0U26Dn5UPv6AuUdakvQZKVJ6jYaLY/FTiFaXdl50+2+kDqhhST5ZFakX9oCGghFz skhgj2lJUD4A1Gkh2K13TTycpSopx1Cga8N2O5x/WjukEc/VUU074nFTh/eloakY aUsZHbsY8xWu0xoK8hJjTIJUegbkBKvDNS4zQWIhi46nt3NMuT+e5W8edXUajub4 2zIcCUOn38VP1FO9egrQ+gmNIWM9MLChVNXDlAJKZDax3BScUtmh2KiDFh3p9UY6 SjOOhO4+iu7CfgDWo7w+s4b3+g3mAo+0EtbgPCj9Oi34D/pEaMjtE9FNq51stXO7 w0BD0RagnvUmluwsVsW0XOAMWjWLzIT7LcgLRjx5VdTduJ8L14syFcmx1wpCvLka ZLt6Yfb2yrelYPUKGfrQLqq12iWtDsCCYbuPWUydufCrU49jtMzEcWNcWtzF2000 tsdVNoWk/qK04vHu1ZCLjZprHvKBvA+VBjzmpbVziXOZs7krVvHga5K1fektlFxt 8Cck/wB9FAPiKr+GHA1YnFLQN3TtXMbbJ6pfZKSK0UM6NvIBjTYpUvmOzeAPgaRr 100pcF/1hpUMrPNTkV4p5/Cqi7doOSCUXS629WeSXWwseI7qXjRLHtK4ew5SMxpq v+YBQ8qlJqJp6S2oL09r5sHqltUlTZ8DyqUtCbCdj9oZ6PtTdNMPN9ylIc2+AUK1 Y/G7Qt0XsuFueY3cip5hKx4ikO1rK+oTtcmJfT7nmkrz413VqqNISBNsNve95bQW yfz5VVREP9M7hFqFeN1p7VfLJHZK/SvbnCnQd1QVQZGzd+KPKChXz8zcNJyEkSLX Lik/iZWFgeNWGY2nspNu1JMiEnmHmSkD5pNUoJ9hY4pvAKK4k+hXhaPd2re6sGZw GvLWfR5cSQPiUnzoZgz9WRQr7J1yxJS2PVT6Xjl8FVuQtfcU7ad7rCbi2ocgW0q+ YKTmh430w2MeZwh1TEWoC2LdA72lBQNY0jRN4hJK5NtktJHUqaVgeVMSNx8vURQR dtLnlyKmypJ8CK34nH/S0lGyfCmxieRCmwsUtZ/B2ItVtWkHLasD8uVeEQnmnAtj e2pPRTZKSPCvpJGtOGt7ZSl2bbcHmEvI2Hn8qso0joS7JPogiKKu9h8Z+tS7XtDs +eoeotR2zIj3GWkHkQpRUD41oDXt6cQlubHgzUp7noqefzxTlf4PWlxRVHnPoSeg UAqsqRwceTvMeYw4PwhSSCaFOgFZ9uaemhRuekY6VE+1CcU0fCvwsaCmJTtTc7Y5 nmtWHQKNZPCq8MZxCS4P92rNZEnh9OY5vW19H57CRV+ZhwVYdtZbVm0a+Q2ceql4 qbJPjiiCHP4lWxKfRLzFuSP3Q6lz686FpGkFt81JUkjplJFWYukpTyUGA3K7Ue0p vOKXkT9lew1Y4ka7tqwLppzt0e9tsjPzHKtqDxqtDig1cbdMhu9FDbuANZ1u0Lq1 phsxL9KYUQCUvHcBRBbtGX5RP21cLdNST+KICfGmnjftCo0mtf6QnJAXcY6c9zo2 1aSNLXU7mpUNwn9x4fxqo7w103Kyp+A1vPXsxtHhWLK4MWN1RVGmTIx7tqs4qWsX ViCd3SNteR90tQ9xBzWZI0Il1JAdaUO4KRQ0vhVqKEsm06vkIA6Bzdy86prj8WbE 6sNSftJpA9pSUqCvh31Gi6YFqdw4J3g24LH7yKD7loJqOSDHfZwe8GiBfFTWlpWB c9Ndoke1htSD+oq/E47WZ4bLnZZsdXfyCxT1kArZelQ2vDCxu6jNSnOzxA4bXgf0 iTEZcUMESWigj51Kf9fA4AJ7gVCmK32jU0V5s+yFYyfCsSfwM1VEBMZliUO7Y6Af OqMXQCXiF2HW0FZz6oLqmlA+NaybDxaszZVCurkloDOWZiXPI1pp8JBGbw31VA5S bLJSfcgBf0rEesU6J6r8V9o+5bZFM1HEfipp9vNwt632/Zy/EKh4pruzx8lEhq+a XhvD8W0FJ8FA1Li0AozDdTzwg/GvbD9wiEKjyH2SnoW3VDHnTqHFDhld0g3PTTjL g/cjpI/ymu7cXg7enMR7kYi1dEbijHiKLYCki6t1DDX6lzecHudAWPOrR1rLcA9M tdtk+/cyEk/MU1jwf09PQpdo1Aw+SeilJOPCsuZwLvCSTGfiPo6jCsGhTaFQvkXb Tcn/AFrTamCfxRX+/wCBro1H0knK412usJ0nkCjIH+GiCXwm1JEb3/Zi3Eg4+7IN DcnSc6M4UPRJDax+Etqp+VhRuxHLzHATZeIJIRzCHZC2/lhWaJ4+suKEBKCpUKeg DokoXn5g5pWOWN9Jxg/AivKLbLjqy2txtQORtUU0t0/aDkcrfGjU1vQn7W0oTk81 NbkjzogsnGu1XWSmNItc2K6r99ORSLF61JCRsRcpe33FW4edEFplajvcRSloZcKe RcUhKFeNZ5JRSui0mfRd5b9KtHbQ4jL7hAUlK09RVfS90RPhlBiojPNnattIxg0v NE64lRZP2TdXANpwhSj5UWq/qzVLclC8Rpg7jy3V5j/X/R2Q/PcWn/wORUrw2oKT kHOa913xdqziJUqVKoCVKlSgDMvVukXCIUxZRjvgeqcApP5EUir/AHq522a/Eudp tkotqKSpTACj8xX0RQXqnQqL7LMxhxpt0jCkrTyJ99VGTQ0rEM5e9LSjtn6YW2rv VGexj88GpR1cOEd3JUppuM7+SV4NStlkJ1PnssOIJ949xq5Eud2g84s2S1/7XCKf Kb7wYvwHbxWobqh1U2ps/MjlXQcPeGt7VttOoGmlEZShEhKvrzqbChRwuJGtICQl q8vlA/C4kKB8a22uMN3eTtulotNwHQl1gA0aucBC8lS4N/YdT3ZRnzFDdy4H6pjl QYZjyQOikOYz8jSjIXJnfy40TPUBc9EMIOea4ju3Fd1ROEl1JLU262tXuV66fOsG bw31PABVItMkJHUpbJFYrlkmxiQ8y4z/AMRBTWmwWHTHDuxy2+1sOuooKj6iZH3a j51oxdD8TLatK7Rf25aUjKTGnhXkaVqoKx1KVfCvcd+fb1bosmQwR/duFNG4WNlO quMVh3plQpEhKTzU7EDg8U1ficd7sw52V504hIHIq9ZB8CKW8LiFrCApJavcshPR KyFDzrdY4x34p2XOHAuCfc8wmio9oLDxHF3QV1SEXWyONKzzPYpXj5irTM7hRfHE lqUIzh7juR9eVAC9f6MuaNt30MzvPVyIsI8K5B7hTczhDV5tThHUq3p86lRiykM2 Rw70tMjOyLfe0hKU7v7VKkj40obxIVbZyo0aSF4OAWz1q1cNO6ft9tcmWTVqZueS o+wpX88cqG4gV6YHCd2D31z5Uki4vkNrboLUF9hpmRpLaHMggOKwaMYydQW+xrg3 iMrtGPXYfHMZFEOh7g09bmUpGCU0fpbafa2rSlQ9xFeeoQzcPg7vP4kuAQ0fq9u7 wQh1QS+3yWk8jmjJl5LqeRrMOmLR6QX0RENunqpHKtJmKhgYRnArqxRnBU/RzZp4 p8xVM71KlStznJXCUh9xgpjuJbWfxEZxXepSasCi08phxEd0qWsjO/HWulwVITb3 1RNvpAQS3u6ZqzgZ6VWnNregvtNr2LUggK91SkoIq7Yo5nEvWlrcWJGn23kIOCpK Fc/CpS4vVzv0O4SG2rjIRsWQNquXWpWycaLaSfop/bXDe4rPpWnLhbt34or+8J/P BrsjTXDua4fQdZPw1H2BJjHzIrMuHCzVVu/t7TI+KE7h5UPv6euEUqEiM82E9dyC P0rbYxGDC0VfY33mmtbwH8H1ENTS2T8jyrUEzjVY0qSn0uY2nHrhKHx4jnSe7Bxo +qohSe8HBFaMS+3+CoLi3Wc2R02vq/jRsn0A1muNmt7Q2EXjT7bhT7S1tLbz4cq0 4/Hqy3BopvGmOROFBKkuE/IgUtovFfWENnsH5qZaM5xLaDn1rQHFZmY8F3bR9jmH GCoNbDSqFgMVvVHB+9oSJMVqE4T+NktqHzFdTo3hjfDm23xpsjqEvg+RpcN3/hlc 1lM7TMy3qPMuRniQD+QrqNN8Mrg4pcHWEqBuHJqTHyEn409Y/RB5J4GMPtqVbb00 4M8t6MjxBrAncD7+wD2BjSfdsVj61SicPru20XdM68hyVZyhtmYpoq88ZrWjReMd lRvafkzUA8gXkPj60tfjGCEvhxqGCCX7VIAH7qM/SsV7T8mOr76O42fcpGKZo4ta 7tGEXXT5dCT6yzGWnl39OVaUfjjZJaki5WAJKjzPqq8iKThJAhN+hejoVjIJ7q7Q jho7k86ZWu9VaTvFrBs8FtuQTlbgZ2KH5UuYxL4CWk5JPLArmyJ1yXAN9EasRa5H YyFbUjkCTypw2/U0Z4Aodzn86REPRl0lFLiWFEnmAKMrfDm2wpakMrbIA5mvNnHV 3FnfBbKmOFq6trAIUOdWhJSWyoEUCW5x1zaAVEZ76JkJU3EcWonATWmPPJ8MWT88 F6LibiO0wcYq2iShY5GhyG0qSjeFdTWo1GWhIwauGSbIy4ca4RqhQPQ1+1mffJOB muyPSCK6I5P8Od467LRcSDjPOuEl1DbKlOLCEAc1E9K/EsKCtyqwb867IivtFh0R dhC3Ep9YfAd9Ty3yOEE37BeVoPTN4eccYvqO0USojck4J+dSgKdprSL0laWtXOQn 1cyh9kpwfjUrpWPgJWnVnNPFDidYNybpae1Sn2i9EVjxSauxf2gAslu96YYWk9S2 efgoUurfxT1nbUpQ3dluIT3PIC8+NbbPGKdJSRebDaLjnluUyEHFbLV+0YBt/OTw vvKOxuVgXFB5lYjjr8U10TYeEV+UHYd5MRahhLfbbQD+aSKCFas4cXEBM7Rb0VR9 pcV6vQs/Cm6JJYvVztiz+F9veB86NF0Abv8ABG1z/XtN+ZeBHRWD5isGfwKv7IJj iLIA/cXtJ+RrOZ4asuJDundeQVZPqIcdLSvrWkzZOL2n2wm2XRU5nqCxJS8B/io1 f0YMXDhZqa3p3O2d8pJwC2N/0oak6fmRFlMmI+0r3LbIppfzncUrGB9qWMutpICl uRFDPzTyrQa4+srXsu2lTuxhW0jP+YUtJCEiILzSt7RUkjoQcGtC33W/2xQXEukx kg5wl9WPDNO0cROGF6aH2jaFs9/rxwcH4pNdUWPhPfWyqBdGI7ixkDttpT8lUv6X QCxh8V9bQm9i5/pKc8w+gKz+VXlcW3ZrJbu+k7PMUU47QN7VD86PVcGLPNZ322/N ug9FHaoeVYczgde2t3o70aQnPIhW3I+dTswFu1NRc5y0IYSyHPZQjoPyo10ppeZC mpkOsF1gjKeVDdx01O01dyxLZUy8363vGPfW/H4wXexx0xWI8RaW04BW3k+NY5E5 8GsHQ97IWvR0Es9mQMEEVqSYsJ1re8hvA71V88tftCagQrLltgLHuwRV1P7Qjr6Q idp5hxPfscP61gvztL2W8lu/Q4lOQ2l4aU3/AMtS7TOysElxJ5hOBSxh8WND3I4l xZ9ucx1QcpzRaxedOXiyuRI2omtq+eXhhQH51g/zZEzbzRdWddLXhtxBZU764/Oj qM4laMgilM7/ACOsCVPzL4p1XujpzWavjFpW0PKEO3XSSQPVK3AEn5ZqsX58idiy zjMeYSnrgV7HKkAP2iWAMDTrn/yK0Lf+0Lb3SBIs7zIzgntAcV2RtezlodpUAoJ7 zVVNwjLdW0Fex7RPQUHQOKNmucVUlhK9oTnJ91D1413Gt0pLyoy3Ybg3KCe/NTtz SLjjsGuLV5ts67IjwUNZbT67iUj1jUrVXrvhhdUhNwtrjKz1UWenzFSt0pUJmPK4 ATVEqgXaC+nHILBHmKHp3BXVMXeUwG3gnvZczmtiNw01TCy7pvV8aSUc0pZmKST8 skVcFx412HAXFdmoTyJKEugj5Vpr/pkLeXoK+wl7ZNrlNHuy0TWS9YpjCiCFJI7l JINN1HGvWEBWy7aYbXg4JUhaP/ytNnjTpG4rUL5ptTCiMFWxLufAZp6yXQxDGA8k gkjd7wK7xp11gYTFly2ADn7pwp50+0XPg3qDs0lxiI4rkEqC2jn6V1PC7Rd0bWq2 39vnzTtdSoDzqNmApoPFHXUHalN4cdbSMBMhtKwfjW03xiuTxAvNjtE8YwoqY2qP zovlcCpJG6FdmHUnoFNkedDdx4M6kjlSkRUvpT3tKBz8qakBW/llw+uSiq6aJcZW faciO4HhmuiLXwmu5zHvFxtS180pko3JT+XPNDszQV+hnDtpmo/MtEjyrHVZJbZI U2tOOoKcVW7AYbPDeK/td03r23LIVkJcUWz5H9K3Y9q4sWkqMSe3cWRjapD4Wk/A Gk63bJCFHswoK/2eVXI03UFrXui3Gaxg5wh0gZ+FS5X7A29WzNTO3dbt/Zdbkq6h SMDH5UET23CorUORrduV8u10eS7cpjshxIwFOHNVJBS5GOR176zbGgaPKvIJFXHm U5O0g1x7E9MVLYHlt3CvW5imhw90FO1hH9IRI9GYScBRGcigi0afduDiSpJDYPXH Wvqjhrafs3TrXqbAUjAxisZZFeqKUeLEZrrR0/TcoRJEsSGsbkLAxS6eBQo5JJr6 14kaOOpLX20dOZTI5JH4hXzNeLC/EdWgpIUk4IPLFa3RV2uAdCj76/CskGva2nEK IKTW5oywnUGo48ReOyCgpefdUuVK2Qk7GDoO1lOl2nnRgOZAyOoouu8iHZLE1Ldj IfVySltaeShWnJhNx/RbXFKGylshAPTlXjUWiblqK0R/RZDTrzKdqkhWEn4Vhjbl Kzr1UY8i5kar0ZIBVcdIlKj7S4zxHlUqrdeFuqGSr+qH1Ad7RCh5VK9JTdHI/Yvm PtGGvfGffaPeW3Cn6VuQtcaytikmNe5wSnolbm8eBpvN6i4P6jUEPMphOYz67ZbH j0rsOHXD6+c7RqFKFK6JS+lXkedSpfSQChcbNUobDc+PAnI70yGPa8Kufzp6enE/ begrc44eRXHwOXzFEczgPIUlXoV0YfR1G8YPlWBO4H6iYaK2mmnsdzboJPyp7IDw ZXCK8NntoFyta/e2Sa/EaG4f3FzFo14uOo/+HIRg/pQ7P4eX23qUl+3yUKAycIzy +IoedsMhtRJSsE/vJxRsA12uG+tYjXbab1smUhP9mluYRkeOK7tu8bbCFBxDtwTy O4lDoH0NJ9uPOhncw680R0LThT9DWvC1rrC1KBZvU5KQMAKc3fWmqAaX88GtLaQL rpVBQOSlFK0HPmKtM8YtMXBRRddMraCvaUUJVzoFicadXsYTIciS2x1S+wDn5itV njBap7iUXnRlvfCuSlM4B86VR+AHUa9cLbutLhSzGdP4VIUjHhyrsrhvpC+b3bfd FErORsdCgPlQEq+8JLmkofs1ygKUea2ugPyPSvEqw8Pm4SpNq1rcoihzCOavIAEU qXQBVN4FbwDGuqSf943j6UudXaPf006uHIUhSwMhSDyIri1rrUFhfP2XqeTJabOE CQNwI+BrNuurbvqZ0v3J1DjqhglKdo8KhqgBchIcKVHlXpbiUABASa8SGiFkg86r hKietZsY0NMaxtLEWNBehobXkJ7THfX0dp2THdtMcMrScIGcV8SJ3JOQa24Gr7/a 0Yh3WQ0ByACsgVzeNqWyLTTVM+yLpe7bZY/bXCY0wju3HmflSh1wizypibgYoehy RuQ4gFOT30B6JtV11texOu0519hshR7RRO8/Cnvd9Nxpuk3oKQMto3NnHskDupTy NvU0jFJWJZuw6QuCFeu8y73I3VZsFtt2kpEia06Fkp5KUeYoLuYdiy1DJSpJ54rO aemTpbcdLzhSpYB592azqXb4LVJjcWtepoyFuT24EhQJbW4raCPjVVvTXEi2KC7H fWpTQOQhuWOfyNc9S6alSocdERxvLbQHZ5x3UuZdovVrfUnMhtSeeW3VAeVdX55Q SoWTkaCtYcXbIf6balPJHeqPvHik1KWcLWeqbdj0e/T07fwqc3DzqV2rU5Q1buvB 27/61ZZ1seUeZQSUjwNdmdB8Or3lVo1euKR0S+ACD8Tg0LXDhhqSAD2lskJA6lKd w8qwXdNTWge0bdSR3qQRUJsY02eF+q4Z7TT+tmnwPYCZZTy8xXcucbbA0rITNab5 5IS6VD60oEQrlDI7JTiccxsUR9K3ImutZ24jsL1OTt5AKIUB8iKL+gMVjjDri1DF 70uHUj2trS0H6EVoNcbtLTQGLzpp5onkr1EOJH0NBcfjdq5hARKEGYMYIeYxnwq5 /O1ZZ5AvGh4MknkVtYSfMUcPoQaNXbhJqJ1RHZsLCeYKVNj+GawdRWrhkwyosXl1 C8cg0O0FC98uWjZbW+xWR+3LUMrC1ZBPwzQJOeKlHCuVLgZoT3bMy4oRHFuozyUp OKzFzImSEIPhVI868EcqmwLReRjlyriXjzAUarkV+YxStiOoWrPWr8d9SU4x1rMS o5ruw8UHnSsCy8oEnNVuSTXVSt9cVc81AzwtQFeAoEYr8Uk13jWybLGWI61j3imA ZaZ15frRFTFtMOOpLY5nYSfnRAnjRqhsqZejRVFQKSkJINBMDTV7RkMvNR9/tZdA 8a37NplMO4tvXCZGddChgBeR86ylGF2bwUgcuF4fmyVuPNFC1nOMUccN9NremouU xshA5oCh1o/i6J07dlJlLDQdT7iMGtdyK1a2ihpaNgGBisZyVcGqg75Mma4hUlY6 AHArLkutYUlaQoHkcjNWXlJWpSveay5Ccg1y92dCjFoxpOl7XOJKNzSj+7Uq+kba lbLLNL2T4ofAgPGq82xYZvOj5QVj11NhScfIir0fjVoa5fdzobrGR6weYBxS5h8b dVsL/pkeFNT0wtvBHzrRHFTTN1bS1e9FRSScrW1jr7x316NnmjBRO4UaiSdki3Nu dM7i0oV7PDHR1yRmDPPPoW30rpdF7g/d3Cl6JKtqnBjcknamu0bQujpCkqsGvFsn PJLi8YPlQARTOBSVFRj3Ftz3BaMGhu4cGr1CSVtxkyAATlpYOPlWn/JLiNbQfsPW SJrecpSqRzPyOfrXh3U/F/T8VX2lbWZDOMF8pB2/nlJpgLG4xXoC1NOoKFJ5EK7q HJCiSTmiG83GXcHXHpLaUuKOVbffQw6SQakDzvIr938q2NFNtv63sjT7aHWlzWgp CxlKhuHIjvpt37R9tsFj1/cXbew416cwYqSkDa0VJUoIP4QdxTy91ACL3ipuB76Y XEfTundNW6Gm1t7pFxeXLZX2hV2cQgbE4z1yTz68qM5llYnTNGWiRbLOLJOaih4t JQiWtzsio5I9bacde+mIRYFegnnTAl6Xs7T2hEojKAurq0zPvD64D+wfD1fdRL/I 6wp1zNtcjTAjFmOtVviLuCv6wIcxuznIO0EhPfSATyT+dRQpjapg2iDw4kqtcUoQ jUbrLTj7W14NhAwhRPPkc8jS3S4D1ooZ4UMV0ZmSWB906pIHurQtdqN1e2B1Lae9 Ro4h6D0+ljfLnOKPeQqpbSGrvgXv2lKOSt5XPrRBYrNerwntokd1TY/FjkaY1k0x ouK+hSWRJcTz+9Oc/KmfBuVqjMJS00y0hI5JSkACsJzXRunJdiqtFm1LD2FSFNtj qSegrbkzZO7sXcnbyye+u2stdNP3GLZba6kekLCVrT3flWlqKGiMY45EloEn3nFZ ODfJe/0wd+U1VfOBX4t7aoiuEiW20yVLIz3CsXFmsZ8HNaxipWSJDqySrlk1KFFj 2C248IYTx322YUj91xOfMUNS+Et5aUezaafT70LA+tSpXrHmmHK4fXdhtRVbpHLq Nmaw5GmpzRG6G8g92Wz/AAqVKQzmY11iOhSXZjSxzBQtSavjU+qWoS4artNVHUMK QslWR8TUqUwMeRIedQd6VEn/AGTWWpClE5Qv/CalSpAu2KabNqC33Mx1upiSEPFs ct205xnuo0vnE2TfNPy7U7bnEh5jsQsuZ2ntu0yRjnywn5VKlAApqK8rvwtYERbP oMBuHzOd+0n1unLr0rZTrYjWNiv32a5i1RmWC1v5ubElOc45ZzUqUxFlOt4C4FjT JsUlybZ1lTDyZG1PN3tDlO3n7q6J1tZRqOZczpqUUTgVPhUnc4hztN4U2op9Tpj4 GpUoAydR6rGooUxCre+zIk3Fc0kPKLaQRjbs6Z5e1QqELH4Ff4TUqUAdG1vtf2fa JP5A13E+4AFPbPEe7nUqUmkB2j3a5RXN7bjoPwNao1TdHWihal59+DUqVOqKtmjo uFJumrGH1hZDZzkg9c06dXysPMN7cqDfM4qVKJJAm7AKU+pJOEq8KznXVOe0lRx+ VSpXM0joi2cys4xtOfhUqVKii7P/2YkCNgQTAQoAIAUCZ0teqgIbAwULCQgHAwUV CgkICwQWAgEAAh4BAheAAAoJEEp1iDzBsdNMxsoP/2amun27Yf9/9lXVZJUagfkm 5M4dBPDoC5YfR7IQ1kFjvexC5vSEQRcD8w/hxyrAlqdYOZqZ8K30S8DS5XFlo0DV O/UXSiglaaTHpZIBkiZwutB5BJA1BzGdj0CsQZnOc2lVaJQoZg29k1TBFvinO1tQ t5o2ue4GMg20CjNjDG7QmQ+Dex1rNSIlbusEPeNybyLZVoRsAEAWirwZ2khAwuxo S+EUs3hTRTXVuhg0Ed9zL4nvV3f8WiUoK0fTHLj5Esx8DBiB/IXZCGGRZziORupe xeugX7kOx5eRpmok7rxZIPIUEfBpC5Zr0EysVa6lh9b6U11eDPFZfNkIUAYJboj7 MvvvJkviA8kg8xEo4oe2eMrwOvMKnpPq0xtsOesmdT4iXREEAbndlnOm9L7o1lIn ZvH7fk3K+myDryh/JejgUNiz/Vk8s8JBCsD8vb9P0TdkG8Jy07VoiTcKdDjaNj9T dqjXq280OYwb8KprhdQmfSMfVhqOa3X0N5xFxIPutOZHYILenAbLQ9GXpNVhCshm ApW8F0cHqoPJXLyIyAQQRgib2zmUfY8aZCgxd5C08HOZMfnY2vdoYZ+tchVoHGIR mpo4RlLFY9ZF6NQW9c+bXJqVXpFNJqtRc2O7YZCs2HzisaudBnx1aFbz2HLDzSU3 ybKi93/CIASzyBkzVpLtuQINBFav2jMBEACxwOSaz5YrOdJ2pp3L/8454ACGhRGX YzKtNgj9gPNT6GyJDHW+x61TN1AeR13MqM5UaIvMrjhE17bh62LhkpBEvg2cRrYB Ge7r8J/8E0Q1i/FeFnjS7PeAGOmT32krDtz0GhcRYoTh6uWBIb3aiYYyU5dufit5 ObSjS3qWHRBdIr2Pie6/ppLOVXdeDsbtscU63HkujRMljYd4uPR6oJwFgdQbySK9 tKU/HUS3qhX8SJ6hEN6rfuzEONWynN36ofDS74W2srZxXF5rz7XxYMUe27+9sZd0 zlgTmXL+3wcUfyCTfr3ZxZdx0FL8GY53OrZDQmSCyY667133O/EzVdBLH5vY1I9u d1H2PxoDPQacjl36/mRCpKNGs2Oh52B3NbJ5U7YeEG4OMcA1zC2blih9ExRhi3gD KFcpTXklvJPPS4ffIurdYFTkcWa8Ko+Ck+RHEOl3qXAINrQk9B5M2+eK3SBt5vC8 L/+Ke0ah3vpkuLUV2Piimtgw38eoDw/H/3v+vQ6O5mYLTCqY59c84HZw2NWGaJdX gHZpr2DlwuEMCQkwPWUt53r+8/Sru4LaDjsJv2V6MNTTeYB9e4LfWwZhHA1Us3SU 4A47B5MpNmTXmBxVLfX0qVJfrs0c5726F16cuAqpL8pOQ5+O/UPQ9+F2l/1h3lxK w0I0ZBq4tOqhzQARAQABiQIfBBgBCAAJBQJWr9ozAhsMAAoJEEp1iDzBsdNMGugP /05GhajYg4ES54fn8lcbvnkGm1w5NVP7OS9wzGY/6nDTHX8rmMvVFBYQXerCBZEo IihXPBTuvQ3vYfXnfwglyRw6QvepLM3oez0iLLJPjQU25SgXutl2EIjVbzYtcmkX DGhUGi7IHSqmjIQumrTQWbHzyUAA58otUh4aPYl4aAKxCOMSJlqzUnOmkZRFIynC 6zxHZvh68G2bv503w7R0S867fjO7qnckRMQI7+MYRfWvTdiwqtw+0dKUkTDhkHIz 4sHHZmWISUXhC1kIA9BoxxVXddL5GoAde0L/62cSXL7HDt1tkA0hhO17is1wu3sm lLUeTvsL7LfXI3bOIQjY1CdlNyf65utFnvFsNNVav2ZEXGYcZH2uvKgY/quIa1+y Cbf8w/aYt+ahoi54NAldvoXE6EPs+bZuDviGLHXCLfQLuMu7NfJyJEkPbxLMf+58 k/bkZ8r7vC+x3EpRSI7oHaYYtoQDsRN2NIrRYwuCXlLt26dIGmmdbzLT5bribw7Q CZYkhjd9jnV7+dpAcVTVrE+A7AXb46JVvFaKrhl6rPIlcB81+XoSg4hvAJOWPvcZ CfWrtHVGvPzOJpNxBQteoYUc1SrVi/1j5WR+FnVDA68pY5QdK3fNSDXIhctNxMxC Yv5/cxSTVRCsTbtFg8tRHkJHhq4FVIk0O8o+TSVrfxzs =JPry -----END PGP PUBLIC KEY BLOCK-----
-
 @ 005bc4de:ef11e1a2
2025-05-12 14:00:42
@ 005bc4de:ef11e1a2
2025-05-12 14:00:42Hostr
Hive + Nostr = Hostr, a bidirectional bridge.

Hostr is a bidirectional bridge between Nostr and Hive. What you post on one is automatically cross-posted to the other. (See SETUP.md if you want to jump right in and run it.)
This is experimental. Expect that there will be glitches, errors, and corrections to be made. So, consider it very beta, with no guarantees, and use at your own risk.
Nostr and Hive have differences, mainly, Nostr is a protocol and Hive is a blockchain. Nostr does not have a token, although bitcoin is much-loved and used across Nostr. Hive has two main tokens: HIVE and the HBD stablecoin. More importantly, Nostr and Hive have similarities. Both are decentralized and censorship resistant thanks to users owning and controlling their own private keys.
Nostr users - why you might want to bridge to Hive
I feel the #1 reason a Nostr user might wish to use this bridge is to permanently store and chronicle your Nostr notes.
-
Immutability for your Nostr notes. Your notes on Nostr are held on relays; if they go away, your notes go away. (There was a “nosdrive.app” backup, however I do not believe it’s still working.) Hive is immutable. There is no "delete" and even an “edit” on Hive does not erase the original. Like with a wiki page, a Hive edit shows the most recent version, but the original still remains historically. This would give Nostr users a permanent record of their notes in chronological order.
-
Hive is an excellent long form blogging platform with stable and persistent links. Finding old Nostr notes can be difficult.
-
Increase your reach and potentially gain followers. Your content will bridge off of the Nostr island and be opened to 10-30,000 daily Hive users. Go to https://peakd.com/c/hive-133987 and look for “Hive statistics” to see numbers.
-
Earn rewards in HIVE and HBD. “Likes” on Nostr do not reward you monetarily, but every upvote on Hive yields rewards. For bitcoin maxis, these tokens can easily be swapped into sats with tools like the https://v4v.app web app, or others.
-
Help grow Nostr. Every note that bridges over to Hive will have a footer saying something like, “This note originated on Nostr,” with a link back to your Nostr note on njump.me. On that page, a "Join Nostr" button is prominent.
Hive users - why you might want to bridge to Nostr
-
Increase your reach and potentially gain followers. Your content will be bridged off the Hive island and be opened to 17-18,000 daily users. See https://stats.nostr.band for Nostr stats.
-
Earn bitcoin sats in the form of “zaps.” Nostr does not have a token. But, it has a strong culture of zapping (tipping) bitcoin satoshis to other users to reward quality content. Memes are loved and often zapped too.
-
Unlimited posting. Nostr is not held back by posting or activity limitations, such as with Resource Credits or community norms that frown on posting too often.
-
Even more censorship resistance. Hive is truly censorship-free in that posted content, no matter the content, does indeed posted. However, front ends can choose to show or not show content that the community has downvoted. Nostr is more free speech or censorship resistant...you post it, it's posted. (Relays can choose to relay it or not, accept it or reject it, but you could run your own relay.)
-
Help grow Hive. Every post that bridges over to Nostr will have a footer saying something like, “This post originated on Hive,” with a link back to your Hive blockchain post. This brings wider exposure to Hive.
Quirks about Nostr and Hive
If you’re unfamiliar with Nostr, it has a few quirks:
-
You have one private key, called an “nsec”. It goes along with your “npub”, your public key. Your npub is your username, your nsec IS your account.
-
You simply need an nsec, then a “client” which is a front end.
- You need to add “relays” to your client in order to connect. This is very easy, but how to do it depends on the client. Client's usually walk you through this when you start.
- Short form content (like the old "Tweets") are called kind 1 notes. Long form notes, like most Hive posts, are called kind 30023.
If you’re unfamiliar with Hive, it has more quirks:
-
Hive has five private keys, yes, five. Each has a specific purpose. From least powerful to most powerful, they are: posting key (to post), active key (to move tokens), owner key (to do anything), memo key (to dm/pm), and backup/master private key (to totally restore all keys). Don’t worry about all the keys. For Hostr, we only deal with posting notes/posts, so the posting key is all we deal with.
-
Hive has a culture of frowning on posting too often. Doing so can be seen as trying to milk the HIVE/HBD rewards that you gain from upvotes. Too much posting can be viewed as spamming and result in downvotes (this hurts your Web-of-Trust score, called “reputation” on Hive, and is shown alongside your username; you want to grow and keep your reputation up). The chain also has a 5-minute cool-down rule coded in: after posting, you cannot post for another five minutes.
-
Additionally, to avoid spam, Hive actions burn “Resource Credits” or RCs. Think of RCs as the charge % in your phone battery. Every action on Hive uses RCs, so they dwindle with every use. Posting is high in RC cost. Bad news: if you run out of RCs, you’re unable to do things on Hive. Good news: RCs also recharge. If out of RCs, you can wait and then do things later. For the Hostr script, over-posting means the script will post until RCs are exhausted, then it will stall until RCs are recharged, post again, stall, etc. You can check your RCs in many places, such as a Hive explorer like https://hivescan.info and entering your Hive username. If you have RC issues, reach out for help.
You don't want to over-post on Hive. To avoid over-posting, Hostr has two versions of the script:
-
bidirectional-longform30023.js
- Nostr ➡️ Hive - Listens only for kind 30023 (long form) Nostr notes to bridge over to Hive. Kind 1 short form notes are ignored.
- Hive ➡️ Nostr - Any Hive post over 380 characters gets truncated as a kind 1 (short form) Nostr note (with a link back to the full Hive post).
-
bidirectional-bridge.js
- Nostr➡️Hive - This script listens for both kind 1 (short form) and kind 30023 (long form) Nostr notes and bridges both over to Hive.
- Hive ➡️ Nostr - Same as above (380+ is truncated).
Which script version should I use?
- If you post frequently on Nostr (more than 2 times per day?), the bidirectional-longform30023.js script is likely best. Per Hive community norms, you don't want to post too often on there. With this script version, only long form notes will bridge over from Nostr to Hive.
- For newcomers to Hive, I would start with this script to be safe.
-
If in doubt, use this script.
-
If you post infrequently on Nostr (2 times per day or fewer?), the bidirectional-bridge.js (both kinds 1 and 30023) might work fine for you.
Nostr users - how to begin
You’ll need a Hive account. You can see sign-up options at https://signup.hive.io. Some options are free, others are not. I (crrdlx) have some free “VIP tickets” to sign up with and you are welcome to use one if you wish, see https://crrdlx.vercel.app/hive-vip-ticket.html. If the tickets there are already spent, contact me and I'll get you set up.
As with Nostr, the critical thing with a Hive account is saving your keys. Hive has multiple keys, just save them all. We’ll only use the “posting key” for the Hostr bridge, however. The other keys can be used on Hive if you wish. (For instance, the "active key" is used to handle your HIVE/HBD rewards earned, the "memo key" for private messages.)
Once signed up (and keys are safe), you can adjust your Hive account/profile using any Hive front end like https://peakd.com/username, https://ecency.com/username, or https://hive.blog/username. Just remember, every action on Hive burns RCs, keep an eye on that.
You can learn more about Hive at https://hivewiki.vercel.app if you wish.
See the "Setting up..." section below to set up the bridge.
Hive users - how to begin
You’ll need a Nostr account. Getting a Nostr "account" is nothing more than generating keys. A simple way to do this is at https://nstart.me If you wish to dig into details, take a look at http://nostrwiki.crrdlx.infinityfreeapp.com/doku.php?id=wiki:get-started
As with Hive, you simply need to safely store your private keys. On Nostr, your private key is called your “nsec” (sec, as in “secret”). Your public key is your “npub” (pub, as in "public"). Your nsec is all you need, but just so you know, your private key comes in two formats: (a) your nsec, and (b) the “hex” form (same key, just different forms). With the Hostr bridge, we’ll use the hex private key. Depending on how you join Nostr, your hex key may be given to you at sign up. But, even if it's not, you can always check back-and-forth between nsec and hex keys using a tool like https://nostrtool.com and choosing "Load a privkey from nsec/hex".
Again, just save your nsec and/or hex private key and you’re set.
You can learn more about Nostr at https://nostrwiki.vercel.app if you wish.
See the "Setting up..." section below to set up the bridge.
Setting up the Hostr bridge
To set up the bridge, see SETUP.md in the repo below. The Hostr bridge has a bit of technicals behind it, but don't get intimidated. Because technical things change, I’ll keep the technical how-to instructions housed at https://github.com/crrdlx/hostr
Disclaimer
This is an experimental bridge. Expect that there will be glitches, errors, and corrections to be made. So, consider it very beta, with no guarantees, and use at your own risk. Source code: https://github.com/crrdlx/hostr
Built with ❤️ by crrdlx
Connect on Hive: @crrdlx
Connect on Nostr: nostr:npub1qpdufhjpel94srm3ett2azgf49m9dp3n5nm2j0rt0l2mlmc3ux3qza082j
All contacts: https://linktr.ee/crrdlx
-
-
 @ 58d88196:bec81862
2025-05-12 19:14:54
@ 58d88196:bec81862
2025-05-12 19:14:54Where We Are Now: AI is already a big part of our lives, even if we don’t always notice it. Think about the last time you used GPS to avoid traffic—that’s AI at work, quietly making your day easier. Companies like NVIDIA,are behind a lot of this magic. They make the tech that powers everything from self-driving cars to massive data centers. In factories, companies like Siemens are using something called "digital twins"—basically virtual copies of their machines—to keep things running smoothly. It’s like having a crystal ball that tells you when a machine might break down before it actually does. Even cities are getting in on the action—Singapore, for example, has a project called Virtual Singapore, which is like a digital version of the city to help with planning things like new roads or buildings. And for us regular folks? If you’ve got a smartwatch tracking your steps or heart rate, you’re already creating a tiny digital version of yourself without even realizing it.
What’s Coming in the near future:Fast forward five or ten years, and this idea of digital twins is going to be everywhere. Picture a factory that never stops because its digital twin catches problems before they happen—no more delays, no more wasted time. Cities will get smarter, too. Imagine a scorching summer day during a heatwave, and instead of a blackout, the city’s AI system automatically shifts energy to where it’s needed most, keeping your AC running. For you and me, digital twins could become a game-changer in healthcare. Your doctor might have a digital version of you—built from your DNA, lifestyle, and even the air quality in your neighborhood—that’s constantly updated. It could warn you about a health issue before you even feel sick, or help your doctor figure out the best treatment just for you. And it doesn’t stop there. You might even have a virtual version of yourself that can attend boring work meetings for you, acting and talking just like you do, while you’re off grabbing a coffee or playing with your kids.
The Big Picture—and the Big Worries: This AI-powered future sounds amazing, but it’s not all smooth sailing. One big concern is privacy. To make these digital twins, companies need a ton of data about us—what we do, where we go, even how our bodies work. That can feel a little creepy, right? What if someone hacks into a city’s digital twin and messes with its power grid or traffic lights? That’s a real risk we’ll need to tackle. Plus, there’s the worry that only the big players—rich companies or cities—will be able to afford this tech, leaving smaller places or communities behind. It’s something we’ll need to figure out so everyone can benefit from what AI has to offer.
-
 @ c3e23eb5:03d7caa9
2025-05-12 13:00:36
@ c3e23eb5:03d7caa9
2025-05-12 13:00:36The issue I have with the term "mesh networks" is that it is associated with a flat network topology. While I love the idea of avoiding hierarchy, this simply doesn't scale. Data Plane: How the Internet Scales
The internet on the scales because it has a tree like structure. As you can see in the diagram below, global (tier 1) ISPs branch out to national (tier 2) ISPs who in turn branch out to local (tier 3) ISPs.
``` ,-[ Tier 1 ISP (Global) ]─-───────[ Tier 1 ISP (Global) ] / |
/ ▼
[IXP (Global)]═══╦═══[IXP (Global)]
║
Tier 2 ISP (National)◄──────────╗
/ \ ║
▼ ▼ ║
[IXP (Regional)]════╬══[IXP (Regional)] ║
/ \ ║
▼ ▼ ║
Tier 3 ISP (Local) Tier 3 ISP (Local) ║
| | ║
▼ ▼ ▼
[User] [User] [Enterprise]▲ IXPs are physical switch fabrics - members peer directly ▲ Tier 1/2 ISPs provide transit through IXPs but don't control them ```
This structure also reflects in IP addresses, where regional traffic gets routed by regional tiers and global traffic keeps getting passed up through gateways till it reaches the root of the tree. The global ISP then routes the traffic into the correct branch so that it can trickle down to the destination IP at the bottom.
12.0.0.0/8 - Tier 1 manages routing (IANA-allocated) └─12.34.0.0/16 - Tier 2 allocated block (through RIR) └─12.34.56.0/24 - Tier 3 subnet via upstream provider ├─12.34.56.1 Public IP (CGNAT pool) └─192.168.1.1 Private IP (local NAT reuse)Balancing idealism with pragmatism
This approach to scaling is much less idealistic than a flat hierarchy, because it relies on an authority (IANA) to assign the IP ranges to ISPs through Regional Internet Registries (RIRs). Even if this authority wasn't required, the fact that many users rely on few Tier 1 ISPs means that the system is inherently susceptible to sabotage (see 2019 BGP leak incident).
Control Plane: the internet is still described as decentralised
The internet is still described as decentralised because there is a flat hierarchy between
tier 1ISPs at the root of the tree. ``` INTERNET CORE (Tier 1 ISPs)AT&T (AS7018) <══════════> Deutsche Telekom (AS3320) ║ ╔════════════════════╗ ║ ║ ║ ║ ║ ╚══>║ NTT (AS2914) ║<══╝ ║ ║ ║ ║ ║ ║ ╚═══════> Lumen (AS3356) ║ ║ ╚════╩════════════> Telia (AS1299)
```
The border gateway protocol (BGP) is used to exchange routing information between autonomous systems (ISPs). Each autonomous system is a branch of the "internet tree" and each autonomous system advertises routes to downstream autonomous systems (branches). However, the autonomous systems at the root of the tree also maintain a record of their piers, so that they can forward traffic to the correct peer. Hence, the following is a more complete diagram of the internet: ```
INTERNET CORE (TIER 1 MESH) ╔══════════════╦═════════════╦════════╦═════════════╗ ║ ║ ║ ║ ║ AT&T (AS7018) <══╬══> Lumen (AS3356) <══╬══> NTT (AS2914) ║ ║ ║ ║ ║ ║ ║ ╚══> Telia (AS1299) <══╝ ║ ║ ╚═══════════════════════════════╝ ║ ║ ╚═> Deutsche Telekom (AS3320) <═╝ ║ TREE HIERARCHY BELOW - MESH ABOVE ║ ▼ [ Tier 1 ISP ]───────────────────┐ / | | / ▼ ▼ [IXP]═══╦═══[IXP] [IXP] ║ ║ ▼ ▼ Tier 2 ISP◄──────────╗ Tier 2 ISP◄───────╗ / \ ║ / \ ║ ▼ ▼ ║ ▼ ▼ ║ [IXP]═╦[IXP] ║ [IXP]═╦[IXP] ║ / \ ║ / \ ║ ▼ ▼ ▼ ▼ ▼ ▼ Tier 3 ISP User Tier 3 ISP Enterprise```
So its a mesh network - whats wrong with that?
In the example above, NTT can only send traffic to Deutsche Telekom via Lumen or AT&T. NTT relies on its peers to maintain a correct record of the IP range that they are responsible for, so that traffic that was intended for Deutsche Telekom doesn't end up in the wrong network. An intentional or even accidental error in an autonomous system's routing tables can be detrimental to the flow of traffic through the network.
Hence, mesh networks require: * Reliability: peers rely on each-other not to fail (e.g., 2019 AWS US-East-1 availability) * Trust: peers must be honest about address ranges (e.g., 2018 BGP hijacking incident) * Central planning: BGP traffic engineering determines which route a packet takes
Application Layer Innovations
Now that we have a rough overview of how the internet is broken, lets think about what can still be done. The flat hierarchy that we associate with mesh networks sounds beautiful, but it doesn't scale. However, the tree-like structure assumes that most participants in the network rely on an authority to give them an address or a range of addresses so that they can communicate.
Overlay networks
Fortunately all it takes to interact with someone on nostr is their public key. The recipients client will render your signed and/or encrypted event no matter how it reaches them. Whether your note reaches them over the internet, over some other network or via a carrier pigeon doesn't matter. nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr is working on a NIP for that and I'm sure he will share an explanation of how it works.
Bitcoin Instead of a Routing Algorithm
Now that we have digital bearer assets (e-cash), users can pay their internet gateway (TollGate) for access to the internet even though they are still offline. Once the TollGate has redeemed the e-cash, it gives the user access to the internet.
Frictionless Switching between ISPs (TollGates)
Legacy internet service providers use KYC money (fiat) to transfer the cost of the infrastructure to their users. However, this means that they are able to identify which packet belongs to which user. The KYC nature of their interaction with the users also makes it difficult for users to switch ISPs when service providers undercut each-other. Internet users who are on e-cash rails can hop between ISPs frictionlessly since they buy small amounts of data frequently in a granular manner.
Users that have access to independent competing TollGates can switch between them freely, so its impossible for any one TollGate to prevent a user from connecting to the internet. The only thing a TollGate can do is attract traffic by providing cheaper and/or faster internet access.
Anyone can arbitrage connectivity
Now that users have non KYC internet, there is nothing stopping them from reselling access to their internet connection. Anyone who has a WiFi router and access to a cheap internet connection can act as a range extender by re-selling access to that gateway for people who aren't able to connect directly.
Now the route that the traffic takes through the network is determined dynamically by the markets. The individual TollGate operators select their gateways and set their prices when they create a business model. The customers select the route that best meets their needs by selecting a gateway for their next purchase.
-
 @ 51faaa77:2c26615b
2025-05-12 17:34:37
@ 51faaa77:2c26615b
2025-05-12 17:34:37My goal is to share a concise list of questions about OP_RETURN limits that we've answered on Stacker News, as the original thread has become unwieldy with over 200 comments. We began compiling this list about a week ago. I've frequently shared individual links and received very positive feedback. I hope this resource helps us work from a common set of facts and reduces misinformation. I hope you find this as a valuable resource.
I'll list the questions in order of activity and tips received. I've removed duplicates, rephrased some statements as questions, and ignored completely irrelevant questions.
- Users should be given clear configurable options to decide what's in their mempool, why were these options taken away? link
- Won't spammers abuse large OP_RETURNs to bloat the blockchain and make IBD take longer? link
- A similar PR was proposed by Peter Todd 2 years ago, why was it rejected then? What has changed since then, why would this get approved now? link
- Shouldn't we be fighting spam, why are we making policies less strict, shouldn't we be making them more strict? link
- How would someone get around the standardness policy currently for OP_RETURN size? link
- What does "standardness mean" in reference to OP_RETURNs? link
- Will more than 1 OP_RETURN per transaction be possible if this PR gets merged? link
- What are the current OP_RETURN limits and what restrictions are being lifted? link
- Are current relay and mempool policies effective for filtering out spam transactions? link
- Is it true that this type of update could affect Bitcoin's decentralization? link
- Is it possible to stop the abuse of payment outputs (i.e., bare multisig, fake pubkeys, and fake pubkey hashes) that are used to embed data, thereby creating unprunable UTXOs that bloat the UTXO set? link
- What was the main reason /concern to add this PR? ... What will happen if we do nothing? link
- If OP_RETURN still cannot stop all the garbage, why is so important to remove it? Does it affect future development / improvements for LN? link
- What will be the worst case scenario if users still could set their own limits for OP_RETURN? link
- Shouldn't we debate the controversy of this PR on Github since it's where the code gets merged to make these changes? link
- What does it mean when someone says "Fix the Filters"? link
- Will this open the flood gates and drown out all legitimate onchain activity? link
- What can we do to stop spam at the consensus layer of Bitcoin? link
- Will Taproot wizards and other spam companies and projects start using OP_RETURN to put jpegs on the blockchain? link
- If we prevent these transaction from going into our mempools doesn't that prevent or delay these spam transactions from being mined therefore discouraging the spammers? link
- Is it possible to stop abuse of witness data? If so, how? (i.e ordinal theory inscriptions, "jpegs"). link
- Is there any conflict of interest with Bitcoin Core and companies like Citrea, in ref to this PR? link
- Is there any estimation on how much would this affect fees for the average user, considering external projects (like Citrea) using it? Any possibility that this could saturate the mempool and boost fees beyond reasonable? link
- Was this PR initially proposed because of Citrea BitVM needs? If so don't they only need a slight bump in OP_RETURN size, why is it being proposed to make the size unrestricted? link
- What makes a UTXO unprunable? Which projects are making unprunable UTXOs? link
- Why would a spammer use OP_RETURN if it's cheaper to use Witness data to store arbitrary data? link
- Won't large OP_RETURNs allow people to spam the mempool with 100kb transactions and mess up bitcoin for everyone by bloating the mempool and not allowing legitimate transactions in the mempool? link
- If relaxing op_return standardness limit seeks to make 'spam' prunable, then what are proponents of this change assuming about the long-term feasibility of running a 'full' (unpruned) bitcoin node? link
- Is allowing standardness for larger OP_RETURNs a slippery slope? If we allow this won't we continue to allow things that make bitcoin less for money and more for arbitrary data? link
- Won't removing the OP_RETURN cap reduce fee market pressure by allowing senders to consolidate arbitrary data into a single transaction? link
- Could this PR be the beginning of reducing other mempool restrictions? link
- Culture is what protects Bitcoin from external forces, shouldn't non-technical arguments be valid when considering these types of changes? link
- What's the difference between UTXO set, mempool, and blockchain, and how do larger OP_RETURN or witness data affect node resource usage? link
- What is the difference in defining a transaction as valid versus defining a transaction as standard and why do we need this difference? link
- If you're happy with your viewpoint on consensus and mempool rules, is not upgrading Bitcoin Core until it makes sense to you a valid action to take right now? link
- Why didn't this PR get a BIP number? link
- Why is core rushing this change? link
- If there will be a hard fork resulted from this PR (split chain like in 2017), what will happen with existing LN channels? Will exist on both chains with 2 LNs? link
- Isn't this all moot in a (almost guaranteed) future where fees are very high? link
- What is this controversy about, and what is it really about? link
originally posted at https://stacker.news/items/978404
-
 @ cecdc1e8:b6c264ee
2025-05-12 12:41:57
@ cecdc1e8:b6c264ee
2025-05-12 12:41:57GM
-
 @ 09d5c0a0:2ebbe260
2025-05-12 17:08:20
@ 09d5c0a0:2ebbe260
2025-05-12 17:08:20*For some people, Bitcoin is about saving for retirement. For others, it’s about eating tomorrow. __I first shared the idea of a “Bitcoin Privilege Curve” at the Plan B Forum 2025 in El Salvador. And it still guides how I see Bitcoin today—especially here in Uganda. __Bitcoin shows up differently depending on where you are in life. What it gives you depends on what you need most. __In Uganda, Bitcoin shows up as survival and uphill battle towards financial empowerment to the largely financially illiterate community. __Sometimes it’s food. Sometimes it’s school fees. Or even a skill. We receive Bitcoin donations that allow us to feed orphans, support teachers, and build small projects that teach these children how to farm, save, and think differently about money, __They’re learning how to live better. A child who knows how to grow food and save in sats is building wealth from the ground up. That’s what the lower end of the curve looks like: *Cheap transactions: Many of the people we work with don’t have bank accounts and the cost of accessing, setting up and maintaining a bank account is just unnecessary. Bitcoin lets them send and receive money within themselves almost at no fees, a better option than the exploitative fee structure by mobile money service providers and most banks. Cross-border remittances: We’ve seen Bitcoin move across borders in minutes with no forms, no gatekeepers. I can instantly and cheaply pay for a friend's grocery shopping in Kenya by sending Kenyan shillings into a Grocery Vendor's Mpesa straight from my Bitcoin wallet via Tando. Wealth multiplication: Even saving one sat creates a shift. It teaches patience. It grows over time. Bitcoin is a wealth multiplier for most underprivileged or privileged people, we taught Bitcoin and its principles to former students at Makerere University that have now entered the job market, from testimonials Bitcoin is helping them achieve their savings goals faster than their colleagues.
__Now go higher up the curve, and Bitcoin looks different. ****Wealth preservation: For someone with savings, Bitcoin protects that value over time, especially in regions with unstable currencies, the Argentina, Zimbabwe and Venezuala currency devaluation scandals always remind me that, you can do everything right and still end up losing all your hard earned value to mediocre goverment policies. Inflation hedge: Where governments keep printing money, Bitcoin holds its ground. It offers a stable alternative. The fallacy that inflation is a necessary evil no longer holds water, having a currency with a 21 Million coin hard cap enforceable by millions of Bitcoin network participants across the world guarantees no governement intervention. Censorship resistance: No one can freeze, reject or interfere with your Bitcoin and respective transactions. It's easy to assume because its a public ledger, you sacrifice privacy hence transaction integrity but this is far from the case, Bitcoin gives people freedom to transact without interference privately. Choice: Bitcoin doesn’t lock you into one system. You can move in and out of, save, or spend it however you see fit as long as your transactions obey the globally agreed upon, never changing network rules since 2009.
__So no, it’s not fair to compare someone struggling for a meal to someone saving for their retirement. But that’s the point. Bitcoin doesn’t need to be the same thing for everyone.
__With Gorilla Sats , our tourism project, we’re linking both ends of the curve. Bitcoiners from around the world visit our communities and spend their Bitcoin with local vendors. It’s not charity—it’s a circular economy. The people higher up the curve get meaningful experiences. Locals get income, exposure, and proof that their sats are valuable.
__In traditional finance, someone without a Visa machine can’t do business with someone carrying a card. The tourist who can't easily use mobile money and is hesistant because of exchange rates will spend comparably less but with Bitcoin, all you need is a phone even a basic button one because with now Machankura 8333, Bitcoin moves via USSD.
__Bitcoin offers privilege—but not the kind that excludes. It offers access, ownership, and freedom based on where you are in life. So no, it’s not fair to compare someone struggling for a meal with someone protecting their portfolio. But that’s the point.
__And if we build for everyone on the curve, we all move forward.
__If you’re building for Bitcoin adoption, think about the full curve. What’s it solving where you live? And who still needs a way in?
-
 @ 7460b7fd:4fc4e74b
2025-05-12 12:23:54
@ 7460b7fd:4fc4e74b
2025-05-12 12:23:54警惕:那些“帮你”保管密钥的人
—— 多签钱包中的隐形风险与逻辑陷阱
“我们可以帮您设置一个更安全的钱包。” 这句话,听上去就像是关心,其实却可能是一次有预谋的接管。
摘要
多签钱包被广泛视为提升数字资产安全性的“进阶方案”,尤其适用于不希望将所有信任寄托于单一点故障(如一把私钥)的人群。然而,在这些看似“民主化”、“抗单点失败”的技术结构背后,仍潜藏着极为隐秘且被低估的风险。
本文聚焦两类常见却高度隐蔽的逻辑攻击模型:
- 替换 xpub 并接管下一层级地址生成;
- 伪造
k-of-n多签结构,在形式上给予用户参与感,实则实现单人提款。
在未引入 Taproot 的传统多签结构下,这类攻击已能轻易完成。而即便在 Taproot 和 MuSig2 合约模型下,攻击者也可以借助合成结构进一步隐藏其篡改行为。
本报告不仅梳理攻击逻辑,更强调“人性中的信任误区”——攻击者不需要主动索取密钥,只需要维持友善形象,自会有用户主动递交钥匙。更令人警惕的是,在某些极端场景下,这类“被信任的服务商”甚至可能向受害者收取“保管密钥”的费用后再实施盗窃,形成双重获利。
Taproot 虽然在结构上增强了隐私与复杂性,但也使验证逻辑失去了可直观还原的优势。随着时间推移、服务厂商退出市场乃至私有恢复流程被锁死,用户极可能落入无法恢复的“密钥黑箱”中。
阅读本文,希望你能意识到:
真正的安全,从不是托付给别人帮你“多签”,而是你真正理解你签了什么、和谁签的、签名之后将通往哪一个脚本。
多签钱包的逻辑攻击向量分析
以 xpub 替换与伪造 k-of-n 结构为例
攻击模型一:替换 xpub 实现地址劫持
场景设定
攻击者假扮为友好的钱包初始化服务者,主动提出“免费帮你生成一个更安全的多签钱包”。表面上,他为你设置了标准的 HD 多签结构,实际上却在关键的派生路径中,悄悄将本应由你或另一个可信方持有的 xpub 替换为他自己的。
在 HD 钱包结构(例如 BIP45、BIP67)中,用户通常无法直观验证每一个新地址是否仍属于原来的签名组。这种设计让“看上去很安全”的地址,可能早已成为攻击者可完全支配的提款口袋。
攻击结构(逻辑表示)
- 假设多签参与者为
P1, P2, P3 - 攻击者控制伪造者身份
P1',实际替代掉用户的P1 - 地址生成函数为:
Addr = f(xpub(P1'), xpub(P2), xpub(P3))- 用户未验证 xpub 时,成立:
∃ Addr_i ∈ wallet, spendable_by(attacker)换言之,钱包中的某些地址虽然看起来正常,但已可被攻击者花费。
人性陷阱提示
用户往往不认为“地址生成这件事”是需要人工检查的,特别是在使用 Ledger、Trezor 等硬件钱包时形成了“签名即安全”的错觉。而攻击者只需一次替换,就能悄悄监视整个钱包生命周期。
更重要的是,攻击者不需要向你“索取密钥”,他只需维持友善、专业甚至略带“为你好”的姿态。在 100 个用户中,总会有一部分人,在受到“信任感”与“他人看起来更专业”的影响下,主动提出将某个密钥托管给对方,甚至支付一定“密钥保管费”作为安全保障。这类行为并非愚蠢,而是人性的一部分。
这种松懈与依赖,背后深植着心理学上著名的「责任分散效应(diffusion of responsibility)」。当责任从“自己一人持有私钥”转变为“我们多人共同掌控”时,大脑会自动削弱“必须百分百保护密钥”的紧迫感;一旦密钥有三份或五份,人就会默认“即使我丢了一份也无所谓”,由此降低警惕,弱化加密习惯的执行力度。
尤其是在多签结构下,密钥不再是“唯一真理”。你开始认为:“我只是 n-of-m 的一员”,进而产生 安全责任稀释(safety dilution)。举个例子:如果你的 seed words 是唯一的,你很可能将其写在一张专用纸上,藏入防火袋,存放于密封保险箱中;但一旦你拥有的是 3-of-5 多签中的一份,你可能就只是把它存在 Evernote、存图于手机相册,或者发给自己 Telegram 备份——并自我安慰说:“这只是其中一把钥匙,又不怕。”
这正是攻击者渗透的最佳入口。他无需破解密码学算法,仅凭理解人性中的懒惰、依赖与责任下沉机制,就足以发起极具杀伤力的社会工程攻击。
提醒:没有人例外。你的安全不是由数学公式决定,而是由你是否对它持续保持敬畏与冷静判断所决定的。
Taproot 下的隐蔽性升级
在 Taproot + MuSig2 合约结构中:
- 合成公钥如:
P = H(P1 + P2 + P3) - 用户无法从地址推导出其组成
- 所有 pubkey 被掩盖,无任何可读性结构泄露
结果:攻击者替换某个 xpub 之后,哪怕是资深用户,也无法通过比对地址结构来发现任何异常。
攻击模型二:伪造 k-of-n 多签脚本结构
场景设定
攻击者承诺为你部署一个“非常安全”的
2-of-3多签钱包。然而他实际创建的却是一个1-of-3结构,并诱导你保留或交出其中一个密钥。用户一旦信任其脚本不可见性(或 UI 模糊性),资金注入该地址之后,攻击者即可单独提款。
攻击结构(逻辑描述)
- 正确脚本应为:
OP_2 <pk1> <pk2> <pk3> OP_3 OP_CHECKMULTISIG- 实际被构造为:
OP_1 <pk1> <pk2> <pk3> OP_3 OP_CHECKMULTISIG- 用户错误地相信:
user_believes(k=2) ∧ attacker_has(sk1) → safe- 但实际上:
real_k = 1 ∧ attacker_has(sk1) → attacker_can_spend成立条件
- 用户未能验证 redeem script
- 钱包界面(UI 或 PSBT)未明确标识 k 值与脚本结构
- 攻击者拥有脚本定义权,或 UI 权限
人性陷阱提示
这类攻击往往并非“高技术”,而是利用用户对脚本结构的无感。尤其是当攻击者扮演“技术专家”时,用户往往不具备审查 redeem script 的能力或意识。攻击者甚至可以用“给你设置一个冷备密钥”作为幌子,骗取部分 key,并收取额外费用。
多签攻击模型对比分析(无表格)
- 攻击类型一:xpub 替换
- 本质:公钥注入
- 隐蔽性:极高(生成地址完全正常)
- 关键条件:用户未验证每个 xpub
-
Taproot 是否能规避:否,反而更难发现
-
攻击类型二:伪造 k-of-n
- 本质:脚本结构欺骗
- 隐蔽性:中等(需查看 redeem script 才能识别)
- 关键条件:用户不懂脚本,UI 不展示结构
- Taproot 是否能规避:否,合约结构反而隐藏了更多细节
安全建议(基于当前攻击模型)
- 强制在 UI 中完整展示所有 xpub、合成地址派生路径与对应签名人列表
- 如 Coldcard 的二维码验证机制
- 用户必须自行保存每个 xpub,并可验证任一地址确实源自该集合派生
- 多签钱包必须提供可见 redeem script 的界面与 k 值校验提示
- 不接受“帮你配置好了”的 UI 黑箱
- Taproot 虽增强隐私,但也加剧验证障碍
- 若使用合签结构,应避免依赖第三方界面进行签名决策
- 始终优先使用硬件钱包本地签名流程,避免通过 Web 或中间服务生成交易
真实案例分析
1. Coldcard 硬件钱包的 xpub 替换漏洞
2021 年,安全研究员 benma 发现 Coldcard 硬件钱包在注册多签钱包时,未验证自身是否为多签钱包的一部分。这使得恶意计算机钱包可以用攻击者控制的 xpub 替换多签 xpub,同时仍通过所有用户验证。所有接收到此多签钱包的币随后可以随时转移到攻击者的钱包。
来源:benma.github.io2. Bybit 交易所的多签钱包被黑事件
2025 年 2 月,Bybit 交易所的多签冷钱包在一次例行转账中被黑,损失约 14.6 亿美元。该钱包使用 2-of-3 多签设置,意味着需要三位授权签名人中的两位批准交易。用户界面显示了合法的目标地址,并且 URL 与受信任的多签提供商 Safe 相关联。但这是一种欺骗。黑客利用硬件钱包中的“盲签名”漏洞,使设备只能显示交易的哈希,从而掩盖了一个更改,使攻击者控制了钱包的智能合约。
来源:certora.com3. Parity 多签钱包漏洞
2017 年,Parity 多签钱包版本 1.5+ 中发现了一个漏洞,允许攻击者窃取超过 150,000 ETH(约 3000 万美元)。攻击者向受影响的合约发送两个交易:第一个获取多签的独占所有权,第二个移动其所有资金。
来源:blog.openzeppelin.com
攻击流程图解
- 建立信任:攻击者以技术专家或受信任的服务提供商身份接近受害者,提出帮助设置多签钱包。
- 替换 xpub:在设置过程中,攻击者用自己控制的 xpub 替换原本应由用户或第三方控制的 xpub。
- 生成地址:攻击者生成看似正常的多签地址,并展示给用户,用户未进行验证。
- 资金注入:用户将资金转入这些地址,认为资金安全。
- 资金转移:攻击者利用控制的私钥,单方面将资金转出,用户无法察觉。
参考文献
附录:攻击面分析——为何 xpub 替换是多签特有的风险?
单签钱包是否存在 xpub 替换攻击?
答案:否。
在单签钱包结构中(如 BIP32/BIP39 衍生的标准钱包):
- 钱包只依赖一个 xpub,并且这个 xpub 是从用户私钥派生而来;
- Coldcard、Trezor 等硬件钱包会自动根据本地 seed 派生地址,无需输入外部 xpub;
- 用户可以通过设备显示屏确认“这是我派生出来的地址”,不存在外部注入路径。
因此:xpub 替换在单签钱包中不存在攻击面,攻击路径被封死。
多签钱包为什么引入了 xpub 攻击面?
多签钱包(如 2-of-3、3-of-5)需要以下信息来生成地址:
- 所有参与者的 xpub;
- 公钥排序规则(如 BIP67);
- 多签脚本模板(如 OP_2
OP_3 OP_CHECKMULTISIG); - 每个 key 的派生路径(如 m/48'/0'/0'/2'/0/1);
这就意味着,用户必须信任这些输入的 xpub 是来自真正的签名方。如果攻击者悄悄将其中某一份换成自己控制的 xpub,那他就自动成为地址共管人,甚至是单签人。
Coldcard 攻击案例回顾:
- 用户通过 PSBT 模板或 JSON 导入多签配置;
- 攻击者在其中替换了某一参与者的 xpub;
- Coldcard 在旧版本中未提示或验证该替换;
- 用户生成地址、发送资金,攻击者即可随时提取。
攻击面比较表
- 单签钱包
- 不接收外部 xpub,派生路径完全由设备掌控;
- 地址来源明确、签名单一;
-
xpub 替换攻击无效。
-
多签钱包
- 依赖多个外部 xpub 合成结构;
- 用户很难手动验证每一条 xpub 与 fingerprint;
- xpub 替换为高危攻击点。
Taproot 是否规避了 xpub 替换问题?
部分规避,但引入了新的验证难题。
Taproot + MuSig2 等结构通过将多个 pubkey 合成为一个点:
P = H(P1 + P2 + P3)
这确实可以隐藏合约结构,提升隐私,但也导致:
- 用户无法从地址还原参与者是谁;
- 如果其中一个公钥被攻击者替换,生成的地址仍然合法;
- 用户在链上看不到任何异常,但攻击者已取得合约控制权。
因此:Taproot 并未从根本上消除 xpub 替换的攻击面,反而因为其不可还原性使得攻击更加隐蔽。
总结
多签钱包之所以引入新的攻击面,不是因为它“更复杂”,而是因为它必须信任外部结构。一旦你的钱包要“与他人协作生成地址”,你就必须验证“这些人是谁”、“这些地址是怎么来的”——这就是攻击的入口。
单签保护的是私钥,
多签则要求你保护你的伙伴。 -
 @ cb4352cd:a16422d7
2025-05-12 12:18:41
@ cb4352cd:a16422d7
2025-05-12 12:18:41In the early days of the internet, openness was a foundational value. Today, as the financial world undergoes its next great evolution, that same principle is making a powerful return — this time through open-source code, permissionless protocols, and user-owned ecosystems. The future of finance isn’t just digital. It’s open.
Beyond the Institution: A Shift in Trust
Traditional finance has always been built around institutions — banks, central authorities, and regulatory bodies. While these structures offer stability, they also limit access, enforce gatekeeping, and concentrate power.
Permissionless innovation flips this model. Instead of asking for approval, builders create protocols that anyone can use, fork, or improve. In DeFi, anyone with an internet connection can lend, borrow, or trade without relying on a centralized intermediary.
Composability: Financial Lego for the Internet Age
Open protocols don’t just stand alone — they connect. In Web3, composability means developers can build on top of each other’s code like financial Lego blocks. This accelerates experimentation and reduces duplication of effort.
You can build a lending protocol that integrates with a decentralized exchange, which in turn connects to a stablecoin, creating a rich, interoperable financial ecosystem — all without closed APIs or licensing fees.
DAOs and the Redefinition of Governance
Openness is not only about access — it’s about control. Decentralized Autonomous Organizations (DAOs) allow communities to govern protocols, allocate resources, and shape development roadmaps. In contrast to top-down decision-making, DAOs are built on transparency, collective voting, and participatory ownership.
As financial systems move on-chain, governance itself becomes programmable. This allows for more adaptive, responsive institutions that can evolve with user needs — not just boardroom mandates.
More Than Code: A Philosophical Shift
Open finance isn’t just a stack of protocols. It reflects a deeper belief: that financial systems should be inclusive, interoperable, and transparent by design.
This philosophy challenges legacy ideas of exclusivity and control. It opens space for local currencies, niche communities, experimental markets, and user-first financial design. It treats users not as passive consumers but as co-owners and co-builders.
How Beyond Banking Conference by WeFi Embraces Openness
This vision of open finance is a central theme of the Beyond Banking Conference by WeFi. Taking place online on May 30, 2025, the conference brings together pioneers from DeFi, AI, Web3, and FinTech to discuss permissionless technologies, composable architecture, and the human values behind them.
Speakers will explore how openness fuels innovation, and how protocol design shapes access, governance, and trust. From DAOs to AI-powered DeFi, the program emphasizes tools that scale freedom — not just efficiency.
In the future, finance won’t just be smart. It will be open. And that changes everything.
-
 @ a3c6f928:d45494fb
2025-05-12 15:30:48
@ a3c6f928:d45494fb
2025-05-12 15:30:48Financial freedom is a powerful concept—one that goes beyond simply having money in the bank. It is the ability to live the life you desire, free from the constraints of financial worry. Achieving financial freedom requires planning, discipline, and a clear understanding of your financial goals.
What Is Financial Freedom?
Financial freedom means having enough income, savings, and investments to support the lifestyle you want for yourself and your family. It is about being in control of your finances, instead of your finances controlling you. When you are financially free, you have choices—you can travel, start a business, or retire comfortably without constant stress about money.
Steps to Achieving Financial Freedom
-
Set Clear Financial Goals: Understand what financial freedom means to you and set measurable goals to achieve it.
-
Create a Budget and Stick to It: Track your income and expenses to identify areas where you can save more.
-
Invest Wisely: Grow your wealth by investing in assets like stocks, real estate, or mutual funds.
-
Build an Emergency Fund: Save at least 3-6 months’ worth of living expenses to protect against unexpected events.
-
Eliminate Debt: High-interest debt can be a major barrier to financial freedom. Prioritize paying it off.
Why Financial Freedom Matters
Financial freedom gives you the power to make decisions without being bound by financial constraints. It allows for greater life flexibility, reduces stress, and opens up opportunities that would otherwise be unreachable. Most importantly, it provides peace of mind and the ability to focus on what truly matters.
Start Your Journey Today
The path to financial freedom is not a quick fix—it is a lifelong commitment to smart financial choices. But with perseverance and planning, it is achievable. Begin today, and take control of your financial future.
“Financial freedom is available to those who learn about it and work for it.” — Robert Kiyosaki
Plan wisely. Invest smartly. Live freely.
-
-
 @ 866e0139:6a9334e5
2025-05-12 10:41:33
@ 866e0139:6a9334e5
2025-05-12 10:41:33Autor: Bastian Barucker. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
John Lennon besang in seinem weltberühmten Lied „Imagine“ die fast unvorstellbare Utopie einer Welt, in der es keinen Grund mehr zu töten gäbe und die Menschen in Frieden zusammen leben. Die enorme Resonanz und Verbreitung dieser Zeilen zeigt den Wunsch fast aller Menschen nach Frieden. Wie Lennon zu diesen Zeilen kam, ist ein Hinweis darauf, dass es dazu neben geopolitischen Analysen und deren Verbreitung durch eine nicht eingebettete und freie Presse vielleicht noch etwas braucht: Schattenarbeit – ein bewusstes Hinwenden zu den eigenen Tiefen der Persönlichkeit, dem inneren Tiefenstaat.
Was ist der Tiefenstaat?
Mit dem Begriff Tiefenstaat verbinde ich Strukturen, die Edward Bernays bereits vor knapp 100 Jahren in seinem Grundlagenwerk „Propaganda“ beschrieb. Im Vorwort schreibt er: „Organisationen, die im Verborgenen arbeiten, lenken die gesellschaftlichen Abläufe. Sie sind die eigentlichen Regierungen in unserem Land.“ Er verwendet diesbezüglich auch das Wort „Schattenkabinett“. Im Bereich der Persönlichkeitsentwicklung wird der Begriff „Schattenarbeit“ dafür verwendet, unbekannte, aber einflussreiche Anteile des eigenen Selbst zu entdecken und zu integrieren.
Lennon begab sich in den 70er Jahren des letzten Jahrhunderts auf die Reise zu sich selbst. Sein Weg führte ihn zum Psychologen Dr. Arthur Janov, der Menschen mithilfe der von ihm entwickelten Primärtherapie dabei begleitete, sich ihrer primären Prägungen und frühkindlichen Traumatisierungen bewusst zu werden und abgespaltenen Schmerz wieder zu erleben, um sich davon zu befreien. Entgegen stark kognitiv geprägter Ansätze wie der Gesprächstherapie steht bei dieser Art der Therapie Gefühlsausdruck im Vordergrund. Janov selbst schreibt dazu: «Die Krankheit ist die Verleugnung des Fühlens, und das Heilmittel ist das Fühlen.»
Auch der Psychologe und Psychotherapeut Franz Ruppert beschäftigt sich intensiv mit dem Fühlen als einem möglichen Weg, eine Traumatisierung aufzuarbeiten. Er schreibt Folgendes über die Bedeutung des Fühlens in seinem Buch „Wer bin ich in einer traumatisierten Gesellschaft“: „Denn letztlich können nur über das Ausdrücken von Gefühlen die fragmentierten psychischen Strukturen wieder zu einer Einheit zusammenfinden.“
Lennon war es möglich, die immense Menge an Schmerz zu entdecken, die er verborgen in sich trug, und er erkannte dabei, welche Verhaltensweisen und Bewältigungsstrategien damit verbunden waren. Laut Lennon ist „Unser Schmerz der Schmerz, durch den wir die ganze Zeit gehen. Du wirst in Schmerz hineingeboren, und wir befinden uns meist im Schmerz. Und ich glaube, je größer der Schmerz ist, umso mehr Götter brauchen wir.“
Die Schilderungen von John Lennon decken sich mit den Erfahrungen meiner Selbsterfahrung und meiner mittlerweile über 10 Jahre langen Begleitungsarbeit in der durch den Schweizer Willi Maurer entwickelten Gefühls- und Körperarbeit.
Auch in dieser Arbeit geht es darum, abgespaltenen Schmerz langsam und über viele Jahre aus dem Schatten in das Bewusstsein zu integrieren, um nicht weiter von ihm unbewusst beeinflusst zu werden. Hunderte Male habe ich Menschen ihnen vorher unbekannten Hass, tiefe Trauer, unendliche Ohnmacht, starke Hilflosigkeit, aber auch Freude, tiefe Geborgenheit, Liebe und Friedfertigkeit entdecken und ausleben sehen. Selber habe ich mich nach einem einjährigen Aufenthalt in der nordamerikanischen Wildnis, bei dem es darum ging, so ehrlich wie möglich miteinander umzugehen, ausführlich meiner Selbsterfahrung gewidmet und dabei Intensitäten von Schmerz, aber auch Zufriedenheit entdeckt, die mir nicht vorstellbar erschienen.
Der Krieg in uns
Fast immer zeigte sich in den begleiteten Prozessen, dass die im Alltag, in der Partnerschaft oder in der Familie angerührten Gefühle aus der eigenen frühen Kindheit stammten. Innere, überfordernde „Kriege“ und Übergriffigkeiten, die auch das Leben im Außen zum Krieg werden ließen, erwachten zum Leben und durften endlich Ausdruck finden. Schlussendlich zeigte sich meist, dass es einen friedlichen Umgang mit der aktuellen Situation gibt, wenn die Altlast „entsorgt“ beziehungsweise kompostiert, also gefühlt und integriert wurde.
Franz Renggli beschreibt diese Psychodynamik in seinem Buch Verlassenheit und Angst – Nähe und Geborgenheit in Bezug auf Partnerschaft wie folgt:
„Die Erfahrung aller meiner Paarbegleitungen zeigt nun: Wenn nach der ersten Verliebtheit langsam der „Alltag“ in eine Beziehung einkehrt, neigen beide Partner immer mehr dazu, ihre Schattenseiten, ihre alten und frühen Verletzungen auch in der Beziehung zuzulassen. Je sicherer die Grenzen sind, desto vertrauensvoller dürfen diese frühen Schmerzen gespürt und erfahren werden. Wir „steigen dann wieder ab“ in unsere ursprüngliche Hölle der Verlassenheit, in die frühkindlichen Prägungen, wie ich sie hier beschrieben habe. Nur: die Hölle sind dann nicht länger die Eltern, sondern jetzt der Partner oder die Partnerin! Vielleicht könnte ich sie oder ihn umbringen vor Enttäuschung und Wut, weil er/sie mich so sehr verletzt hat. Und damit kann sie beginnen, die Heilung der alten Wunden in der Paarbeziehung! Aber nur dann, wenn wir bereit sind, unsere alten verletzten Gefühle wirklich zu spüren und zuzulassen. Und wenn wir zu diesem Schritt bereit sind, dann können wir auch gleichzeitig empfinden und wissen: Das sind unsere ureigensten alten Verletzungen, welche wir seit der Kindheit in uns tragen – ein Partner mit seinen Worten und seinem Verhalten ist nur der Auslöser unseres alten Schmerzes, ein harter Spiegel unserer alten Wunden! Wir alle haben unsere Partner entsprechend gewählt, damit wir in unseren Grundfesten immer wieder – neben allem Glück, das wir mit ihnen erleben und teilen dürfen – auch erschüttert werden.“
Diese wiederkehrenden Erschütterungen werden auch Reinszenierungszwang genannt und lassen Menschen immer wieder dieselben misslichen Lagen (mit)erschaffen, die ihnen Leid zufügen. Willi Maurer beschreibt diese Dynamik in einem sehr lesenswerten Artikel mit dem Titel „Die verschüttete Quelle des Friedens“ wie folgt: „Die Spirale der Gewalt zeigt, dass wir andern Menschen das antun, was uns selbst widerfahren ist. Doch ohne Selbsterforschung bleiben wir blind gegenüber der tief in uns verdrängt liegenden Wahrheit.“
Diese Reinszenierung ist gleichzeitig jedoch eine immer wiederkehrende Chance, sich der Ursache dieser Dynamik zuzuwenden. Das geschieht dann, wenn die Person sich als Erschaffer oder Erschafferin und nicht als reines Opfer der Umstände versteht und beginnt, die volle Verantwortung für das eigene Leben zu übernehmen.
Vor einigen Jahren brachte ich den Prozessbegleiter Willi Maurer und den Friedensforscher Dr. Daniele Ganser zu einem Gespräch zusammen, weil ich der Ansicht war, dass beide Friedensarbeit aus verschiedenen Perspektiven leisten. Es war eine Wohltat, zu erleben, wie Ganser durch die sehr authentischen Schilderungen Maurers zu ahnen begann, dass es eine Verbindung zwischen weltweiten Kriegen und frühen Erfahrungen geben kann. Was hat der Soldat, Politiker oder Geostratege erlebt, dass er in der Lage ist, Krieg zu befördern, zu verursachen oder auch nur zu dulden?
Vielleicht ist die immer wiederkehrende Kriegsbereitschaft und Kriegslust elitärer Kreise neben der wahrscheinlich frühkindlich erzeugten Gier nach Macht, Einfluss und Geld ebenfalls ein gesellschaftlicher Reinszenierungszwang. Die inneren Zerwürfnisse und Kriege müssen quasi ins Außen getragen werden, um sich dem im Schatten der eigenen Persönlichkeit wartenden Schmerz nicht zuwenden zu müssen.
Eine weitere Bewältigungsstrategie für innere, emotionale Zerwürfnisse ist die Projektion, also die Veräußerlichung des Eigenen auf andere. Ein hier vielleicht Sinn stiftendes Beispiel ist die immer wieder betonte weitestgehend unbelegte Unterstellung imperialistischer Bestrebungen Russlands im Zuge des völkerrechtswidrigen Krieges in der Ukraine. Meist kommt diese Behauptung von Vertretern oder Unterstützern der NATO, die – wie an ihrer großflächigen, gegen westliche Zusagen an Russland verstoßenden NATO-Osterweiterung leicht zu erkennen – offensichtlich selbst imperialistische Bestrebungen verfolgt.
Die Projektion ins Außen
Interessanterweise hat ausgerechnet Präsident Putin in anschaulichen Worten beschrieben, was unter anderem mit im Schatten liegenden Persönlichkeitsanteilen auch auf geopolitischer Ebene passieren kann. Sie werden anderen Menschen oder Staaten zugeschrieben, also ins Außen projiziert. Auf die Beschuldigung durch US-Präsidenten Joe Biden, ein Mörder zu sein, antwortete Putin: „Aber wenn wir andere Menschen bewerten, oder wenn wir sogar andere Staaten, andere Völker bewerten, sehen wir immer in den Spiegel, wir sehen uns immer selbst, weil wir auf eine andere Person übertragen, was wir selbst sind, was uns im Wesentlichen ausmacht. Wissen Sie, ich erinnere mich, als wir als Kinder im Hinterhof waren, als wir miteinander gestritten und gesagt haben: Wie Du andere nennst, so bist Du selbst. Und das ist kein Zufall, das ist nicht nur ein Kindersprichwort oder ein Witz. Der Sinn ist sehr psychologisch. Wir sehen immer unsere eigenen Qualitäten in einer anderen Person und denken, dass sie so ist wie wir, und daraus bewerten wir ihr Handeln und bewerten sie insgesamt.“
https://www.youtube.com/watch?v=7sMAHWH_hhQ
Der bereits erwähnte Tiefenstaat, also eine quasi Schattenregierung, existiert auf der geopolitischen Weltbühne und bestimmt größtenteils die Geschicke, insbesondere wenn es um Krieg und Frieden geht. Der Kognitionsforscher Professor Rainer Mausfeld beschreibt die unsichtbar im Hintergrund wirkenden Strukturen in seinem Buch „Angst und Macht“ wie folgt: „Die tatsächliche Macht ist heute in neuartigen globalen Organisationsformen verortet, die vollkommen einer gesellschaftlichen Kontrolle entzogen sind, die für die Bevölkerung weitgehend unsichtbar sind…“
Gleiches gilt meiner Annahme nach auch für die persönlichen Machtverhältnisse, bei denen eigene Schattenanteile ebenfalls großen Einfluss auf die sichtbaren Verhaltensweisen nehmen. Dieser unbewusste Anteil kann auf der einen Seite Macht über die eigene Kriegsbereitschaft und Friedenstüchtigkeit ausüben, auf der anderen Seite wird er von Kriegstreibern mittels kognitiver Kriegsführung aktiv benutzt, um die Bevölkerung zu manipulieren. Der Propagandaforscher Dr. Jonas Tögel schreibt dazu: „Die Tiefenpsychologie dient als Fundament der wohl wichtigsten Manipulationswaffe: die gezielte Beeinflussung des Unbewussten der menschlichen Psyche. Wie bei einem Eisberg liegt ein großer Teil unserer Gedanken und Gefühle „unter der Wasseroberfläche“, und hier können wir so beeinflusst werden, dass wir die Steuerung selbst oft nicht bemerken.“
Der Tiefe Staat kann also ungesehen politisch schalten und walten und gleichzeitig die unbewussten Anteile der menschlichen Psyche zu seinen Gunsten ausnutzen.
Teil 2 folgt in Kürze.
Bastian Barucker, Jahrgang 83, ist Wildnispädagoge, Überlebenstrainer und Prozessbegleiter. Seit 2005 begleitet er Menschen bei Wachstumsprozessen in der Natur. Seit 2011 macht er mithilfe der Gefühls- und Körperarbeit tiefgreifende Selbsterfahrungen, und seit 2014 begleitet er Gruppen, Paare und Einzelpersonen. Er lebt und arbeitet im wunderschönen Lassaner Winkel, nahe der Insel Usedom. Zuletzt erschien von ihm das Buch "Auf Spurensuche nach Natürlichkeit: Vom Leben in der Wildnis und der Reise zu sich selbst" im Massel Verlag.
Kontakt: www.bastian-barucker.de
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.