-
 @ 57d1a264:69f1fee1
2025-05-24 06:07:19
@ 57d1a264:69f1fee1
2025-05-24 06:07:19Definition: when every single person in the chain responsible for shipping a product looks at objectively horrendous design decisions and goes: yup, this looks good to me, release this. Designers, developers, product managers, testers, quality assurance... everyone.
I nominate Peugeot as the first example in this category.
Continue reading at https://grumpy.website/1665
https://stacker.news/items/988044
-
 @ 57d1a264:69f1fee1
2025-05-24 05:53:43
@ 57d1a264:69f1fee1
2025-05-24 05:53:43This talks highlights tools for product management, UX design, web development, and content creation to embed accessibility.
Organizations need scalability and consistency in their accessibility work, aligning people, policies, and processes to integrate it across roles. This session highlights tools for product management, UX design, web development, and content creation to embed accessibility. We will explore inclusive personas, design artifacts, design systems, and content strategies to support developers and creators, with real-world examples.
https://www.youtube.com/watch?v=-M2cMLDU4u4
https://stacker.news/items/988041
-
 @ 348e7eb2:3b0b9790
2025-05-24 05:00:33
@ 348e7eb2:3b0b9790
2025-05-24 05:00:33Nostr-Konto erstellen - funktioniert mit Hex
Was der Button macht
Der folgende Code fügt einen Button hinzu, der per Klick einen Nostr-Anmeldedialog öffnet. Alle Schritte sind im Code selbst ausführlich kommentiert.
```html
```
Erläuterungen:
- Dynamisches Nachladen: Das Script
modal.jswird nur bei Klick nachgeladen, um Fehlermeldungen beim Initial-Load zu vermeiden. -
Parameter im Überblick:
-
baseUrl: Quelle für API und Assets. an: App-Name für den Modal-Header.aa: Farbakzent (Foerbico-Farbe als Hex).al: Sprache des Interfaces.am: Licht- oder Dunkelmodus.afb/asb: Bunker-Modi für erhöhten Datenschutz.aan/aac: Steuerung der Rückgabe privater Schlüssel.arr/awr: Primal Relay als Lese- und Schreib-Relay.-
Callbacks:
-
onComplete: Schließt das Modal, zeigt eine Bestätigung und bietet die Weiterleitung zu Primal an. onCancel: Schließt das Modal und protokolliert den Abbruch.
Damit ist der gesamte Code sichtbar, kommentiert und erklärt.
- Dynamisches Nachladen: Das Script
-
 @ f6488c62:c929299d
2025-05-24 05:10:20
@ f6488c62:c929299d
2025-05-24 05:10:20คุณเคยจินตนาการถึงอนาคตที่ AI มีความฉลาดเทียบเท่ามนุษย์หรือไม่? นี่คือสิ่งที่ Sam Altman ซีอีโอของ OpenAI และทีมพันธมิตรอย่าง SoftBank, Oracle และ MGX กำลังผลักดันผ่าน โครงการ Stargate! โครงการนี้ไม่ใช่แค่เรื่องเทคโนโลยี แต่เป็นก้าวกระโดดครั้งใหญ่ของมนุษยชาติ! Stargate คืออะไร? Stargate เป็นโปรเจกต์สร้าง ศูนย์ข้อมูล AI ขนาดยักษ์ที่ใหญ่ที่สุดในประวัติศาสตร์ ด้วยเงินลงทุนเริ่มต้น 100,000 ล้านดอลลาร์ และอาจสูงถึง 500,000 ล้านดอลลาร์ ภายในปี 2029! เป้าหมายคือการพัฒนา Artificial General Intelligence (AGI) หรือ AI ที่ฉลาดเทียบเท่ามนุษย์ เพื่อให้สหรัฐฯ ครองความเป็นผู้นำด้าน AI และแข่งขันกับคู่แข่งอย่างจีน โครงการนี้เริ่มต้นที่เมือง Abilene รัฐเท็กซัส โดยจะสร้างศูนย์ข้อมูล 10 แห่ง และขยายไปยังญี่ปุ่น สหราชอาณาจักร และสหรัฐอาหรับเอมิเรตส์ ทำไม Stargate ถึงสำคัญ?
นวัตกรรมเปลี่ยนโลก: AI จาก Stargate จะช่วยพัฒนาวัคซีน mRNA รักษามะเร็งได้ใน 48 ชั่วโมง และยกระดับอุตสาหกรรมต่าง ๆ เช่น การแพทย์และความมั่นคงแห่งชาติสร้างงาน: คาดว่าจะสร้างงานกว่า 100,000 ตำแหน่ง ในสหรัฐฯ
พลังงานมหาศาล: ศูนย์ข้อมูลอาจใช้พลังงานถึง 1.2 กิกะวัตต์ เทียบเท่ากับเมืองขนาดใหญ่!
ใครอยู่เบื้องหลัง? Sam Altman ร่วมมือกับ Masayoshi Son จาก SoftBank และได้รับการสนับสนุนจาก Donald Trump ซึ่งผลักดันนโยบายให้ Stargate เป็นจริง การก่อสร้างดำเนินการโดย Oracle และพันธมิตรด้านพลังงานอย่าง Crusoe Energy Systems ความท้าทาย? ถึงจะยิ่งใหญ่ แต่ Stargate ก็เจออุปสรรค ทั้งปัญหาการระดมทุน ความกังวลเรื่องภาษีนำเข้าชิป และการแข่งขันจากคู่แข่งอย่าง DeepSeek ที่ใช้โครงสร้างพื้นฐานน้อยกว่า แถม Elon Musk ยังออกมาวิจารณ์ว่าโครงการนี้อาจ “ไม่สมจริง” แต่ Altman มั่นใจและเชิญ Musk ไปดูไซต์งานที่เท็กซัสเลยทีเดียว! อนาคตของ Stargate ศูนย์ข้อมูลแห่งแรกจะเริ่มใช้งานในปี 2026 และอาจเปลี่ยนโฉมวงการ AI ไปตลอดกาล นี่คือก้าวสำคัญสู่ยุคใหม่ของเทคโนโลยีที่อาจเปลี่ยนวิถีชีวิตของเรา! และไม่ใช่ประตูดวงดาวแบบในหนังนะ! ถึงชื่อ Stargate จะได้แรงบันดาลใจจากภาพยนตร์ sci-fi อันโด่งดัง แต่โครงการนี้ไม่ได้พาเราไปยังดวงดาวอื่น มันคือการเปิดประตูสู่โลกแห่ง AI ที่ทรงพลัง และอาจเปลี่ยนอนาคตของมนุษยชาติไปเลย! และไม่เหมือน universechain ของ star ของผมนะครับ
Stargate #AI #SamAltman #OpenAI #อนาคตของเทคโนโลยี
-
 @ 06830f6c:34da40c5
2025-05-24 04:21:03
@ 06830f6c:34da40c5
2025-05-24 04:21:03The evolution of development environments is incredibly rich and complex and reflects a continuous drive towards greater efficiency, consistency, isolation, and collaboration. It's a story of abstracting away complexity and standardizing workflows.
Phase 1: The Bare Metal & Manual Era (Early 1970s - Late 1990s)
-
Direct OS Interaction / Bare Metal Development:
- Description: Developers worked directly on the operating system's command line or a basic text editor. Installation of compilers, interpreters, and libraries was a manual, often arcane process involving downloading archives, compiling from source, and setting environment variables. "Configuration drift" (differences between developer machines) was the norm.
- Tools: Text editors (Vi, Emacs), command-line compilers (GCC), Makefiles.
- Challenges: Extremely high setup time, dependency hell, "works on my machine" syndrome, difficult onboarding for new developers, lack of reproducibility. Version control was primitive (e.g., RCS, SCCS).
-
Integrated Development Environments (IDEs) - Initial Emergence:
- Description: Early IDEs (like Turbo Pascal, Microsoft Visual Basic) began to integrate editors, compilers, debuggers, and sometimes GUI builders into a single application. This was a massive leap in developer convenience.
- Tools: Turbo Pascal, Visual Basic, early Visual Studio versions.
- Advancement: Improved developer productivity, streamlined common tasks. Still relied on local system dependencies.
Phase 2: Towards Dependency Management & Local Reproducibility (Late 1990s - Mid-2000s)
-
Basic Build Tools & Dependency Resolvers (Pre-Package Managers):
- Description: As projects grew, manual dependency tracking became impossible. Tools like Ant (Java) and early versions of
autoconf/makefor C/C++ helped automate the compilation and linking process, managing some dependencies. - Tools: Apache Ant, GNU Autotools.
- Advancement: Automated build processes, rudimentary dependency linking. Still not comprehensive environment management.
- Description: As projects grew, manual dependency tracking became impossible. Tools like Ant (Java) and early versions of
-
Language-Specific Package Managers:
- Description: A significant leap was the emergence of language-specific package managers that could fetch, install, and manage libraries and frameworks declared in a project's manifest file. Examples include Maven (Java), npm (Node.js), pip (Python), RubyGems (Ruby), Composer (PHP).
- Tools: Maven, npm, pip, RubyGems, Composer.
- Advancement: Dramatically simplified dependency resolution, improved intra-project reproducibility.
- Limitation: Managed language-level dependencies, but not system-level dependencies or the underlying OS environment. Conflicts between projects on the same machine (e.g., Project A needs Python 2.7, Project B needs Python 3.9) were common.
Phase 3: Environment Isolation & Portability (Mid-2000s - Early 2010s)
-
Virtual Machines (VMs) for Development:
- Description: To address the "it works on my machine" problem stemming from OS-level and system-level differences, developers started using VMs. Tools like VMware Workstation, VirtualBox, and later Vagrant (which automated VM provisioning) allowed developers to encapsulate an entire OS and its dependencies for a project.
- Tools: VMware, VirtualBox, Vagrant.
- Advancement: Achieved strong isolation and environment reproducibility (a true "single environment" for a project).
- Limitations: Resource-heavy (each VM consumed significant CPU, RAM, disk space), slow to provision and boot, difficult to share large VM images.
-
Early Automation & Provisioning Tools:
- Description: Alongside VMs, configuration management tools started being used to automate environment setup within VMs or on servers. This helped define environments as code, making them more consistent.
- Tools: Chef, Puppet, Ansible.
- Advancement: Automated provisioning, leading to more consistent environments, often used in conjunction with VMs.
Phase 4: The Container Revolution & Orchestration (Early 2010s - Present)
-
Containerization (Docker):
- Description: Docker popularized Linux Containers (LXC), offering a lightweight, portable, and efficient alternative to VMs. Containers package an application and all its dependencies into a self-contained unit that shares the host OS kernel. This drastically reduced resource overhead and startup times compared to VMs.
- Tools: Docker.
- Advancement: Unprecedented consistency from development to production (Dev/Prod Parity), rapid provisioning, highly efficient resource use. Became the de-facto standard for packaging applications.
-
Container Orchestration:
- Description: As microservices and container adoption grew, managing hundreds or thousands of containers became a new challenge. Orchestration platforms automated the deployment, scaling, healing, and networking of containers across clusters of machines.
- Tools: Kubernetes, Docker Swarm, Apache Mesos.
- Advancement: Enabled scalable, resilient, and complex distributed systems development and deployment. The "environment" started encompassing the entire cluster.
Phase 5: Cloud-Native, Serverless & Intelligent Environments (Present - Future)
-
Cloud-Native Development:
- Description: Leveraging cloud services (managed databases, message queues, serverless functions) directly within the development workflow. Developers focus on application logic, offloading infrastructure management to cloud providers. Containers become a key deployment unit in this paradigm.
- Tools: AWS Lambda, Azure Functions, Google Cloud Run, cloud-managed databases.
- Advancement: Reduced operational overhead, increased focus on business logic, highly scalable deployments.
-
Remote Development & Cloud-Based IDEs:
- Description: The full development environment (editor, terminal, debugger, code) can now reside in the cloud, accessed via a thin client or web browser. This means developers can work from any device, anywhere, with powerful cloud resources backing their environment.
- Tools: GitHub Codespaces, Gitpod, AWS Cloud9, VS Code Remote Development.
- Advancement: Instant onboarding, consistent remote environments, access to high-spec machines regardless of local hardware, enhanced security.
-
Declarative & AI-Assisted Environments (The Near Future):
- Description: Development environments will become even more declarative, where developers specify what they need, and AI/automation tools provision and maintain it. AI will proactively identify dependency issues, optimize resource usage, suggest code snippets, and perform automated testing within the environment.
- Tools: Next-gen dev container specifications, AI agents integrated into IDEs and CI/CD pipelines.
- Prediction: Near-zero environment setup time, self-healing environments, proactive problem identification, truly seamless collaboration.
web3 #computing #cloud #devstr
-
-
 @ 90152b7f:04e57401
2025-05-24 03:47:24
@ 90152b7f:04e57401
2025-05-24 03:47:24"Army study suggests U.S. force of 20,000"
The Washington Times - Friday, April 5, 2002
The Bush administration says there are no active plans to put American peacekeepers between Palestinians and Israelis, but at least one internal military study says 20,000 well-armed troops would be needed.
The Army’s School of Advanced Military Studies (SAMS), an elite training ground and think tank at Fort Leavenworth, Kan., produced the study last year. The 68-page paper tells how the major operation would be run the first year, with peacekeepers stationed in Gaza, Hebron, Jerusalem and Nablus.
One major goal would be to “neutralize leadership of Palestine dissenting factions [and] prevent inter-Palestinian violence.”
The military is known to update secret contingency plans in the event international peacekeepers are part of a comprehensive Middle East peace plan. The SAMS study, a copy of which was obtained by The Washington Times, provides a glimpse of what those plans might entail.
Defense Secretary Donald H. Rumsfeld repeatedly has said the administration has no plans to put American troops between the warring factions. But since the escalation of violence, more voices in the debate are beginning to suggest that some type of American-led peace enforcement team is needed.
Sen. Arlen Specter, Pennsylvania Republican, quoted U.S. special envoy Gen. Anthony Zinni as saying there is a plan, if needed, to put a limited number of American peacekeepers in the Israeli-occupied territories.
Asked on CBS whether he could envision American troops on the ground, Mr. Specter said Sunday: “If we were ever to stabilize the situation, and that was a critical factor, it’s something that I would be willing to consider.”
Added Sen. Joseph R. Biden Jr., Delaware Democrat and Senate Foreign Relations Committee chairman, “In that context, yes, and with European forces as well.”
The recent history of international peacekeeping has shown that it often takes American firepower and prestige for the operation to work. The United Nations made futile attempts to stop Serbian attacks on the Muslim population in Bosnia.
The U.S. entered the fray by bombing Serbian targets and bringing about a peace agreement that still is being backed up by American soldiers on the ground. U.S. combat troops are also in Kosovo, and they have a more limited role in Macedonia.
But James Phillips, a Middle East analyst at the Heritage Foundation, used the word “disaster” to describe the aftermath of putting an international force in the occupied territories.
“I think that would be a formula for sucking us into the violence,” he said. “United States troops would be a lightening rod for attacks by radical Islamics and other Palestinian extremist groups. The United States cannot afford to stretch its forces any thinner. They’re very busy as it is with the war against international terrorism.”
Mr. Phillips noted that two Norwegian observers in Hebron were killed this week. U.N. representatives on the Lebanon border have been unable to prevent terrorists from attacking Israel.
The SAMS paper tries to predict events in the first year of peacekeeping and the dangers U.S. troops would face.
It calls the Israeli armed forces a “500-pound gorilla in Israel. Well armed and trained. Operates in both Gaza [and the West Bank]. Known to disregard international law to accomplish mission. Very unlikely to fire on American forces.”
On the Mossad, the Israeli intelligence service, the Army study says, “Wildcard. Ruthless and cunning. Has capability to target U.S. forces and make it look like a Palestinian/Arab act.”
It described Palestinian youth as “loose cannons; under no control, sometimes violent.” The study was done by 60 officers dubbed the “Jedi Knights,” as all second-year SAMS students are called. The Times first reported on their work in September. Recent violence in the Middle East has raised questions about what type of force it would take to keep the peace.
In the past, SAMS has done studies for the Army chief of staff and the Joint Chiefs. SAMS personnel helped plan the allied ground attack that liberated Kuwait.
The Middle East study sets goals that a peace force should accomplish in the first 30 days. They include “create conditions for development of Palestinian State and security of [Israel],” ensure “equal distribution of contract value or equivalent aid” and “build lasting relationships based on new legal borders and not religious-territorial claims.”
The SAMS report does not specify a full order of battle for the 20,000 troops. An Army source who reviewed the paper said each of three brigades would require about 100 armored vehicles, 25 tanks and 12 self-propelled howitzers, along with attack helicopters and spy drones.
The Palestinians have supported calls for an international force, but Tel Aviv has opposed the idea.
https://www.washingtontimes.com/news/2002/apr/5/20020405-041726-2086r/
-
 @ 2b998b04:86727e47
2025-05-24 03:40:36
@ 2b998b04:86727e47
2025-05-24 03:40:36Solzhenitsyn Would Have Loved Bitcoin
I didn’t plan to write this. But a comment from @HODL stirred something in me — a passing thought that took root and wouldn’t let go:
> “Solzhenitsyn would have understood Bitcoin.”
The more I sat with it, the more I realized: he wouldn’t have just understood it — he would have loved it.
A Life of Resistance
Aleksandr Solzhenitsyn didn’t just survive the Soviet gulags — he exposed them. Through The Gulag Archipelago and other works, he revealed the quiet machinery of evil: not always through brutality, but through systemic lies, suppressed memory, and coerced consensus.
His core belief was devastatingly simple:
> “The line dividing good and evil cuts through the heart of every human being.”
He never let anyone off the hook — not the state, not the system, not even himself. Evil, to Solzhenitsyn, was not “out there.” It was within. And resisting it required truth, courage, and deep personal responsibility.
Bitcoin: Truth That Resists
That’s why I believe Solzhenitsyn would have resonated with Bitcoin.
Not the hype. Not the coins. Not the influencers.
But the heart of it:
-
A system that resists coercion.
-
A ledger that cannot be falsified.
-
A network that cannot be silenced.
-
A protocol that doesn't care about party lines — only proof of work.
Bitcoin is incorruptible memory.\ Solzhenitsyn fought to preserve memory in the face of state erasure.\ Bitcoin cannot forget — and it cannot be made to lie.
Responsibility and Sovereignty
Bitcoin demands what Solzhenitsyn demanded: moral responsibility. You hold your keys. You verify your truth. You cannot delegate conscience.
He once wrote:
> “A man who is not inwardly prepared for the use of violence against him is always weaker than his opponent.”
Bitcoin flips that equation. It gives the peaceful man a weapon: truth that cannot be seized.
I’ve Felt This Line Too
I haven’t read all of The Gulag Archipelago — it’s long, and weighty — but I’ve read enough to know Solzhenitsyn’s voice. And I’ve felt the line he describes:
> That dividing line between good and evil… that runs through my own heart.
That’s why I left the noise of Web3. That’s why I’m building with Bitcoin. Because I believe the moral architecture of this protocol matters. It forces me to live in alignment — or walk away.
Final Word
I think Solzhenitsyn would have seen Bitcoin not as a tech innovation, but as a moral stand. Not a replacement for Christ — but a quiet echo of His justice.
And that’s why I keep stacking, writing, building — one block at a time.
Written with help from ChatGPT (Dr. C), and inspired by a comment from @HODL that sparked something deep.
If this resonated, feel free to zap a few sats — not because I need them, but because signal flows best when it’s shared with intention.
HODL mentioned this idea in a note — their Primal profile:\ https://primal.net/hodl
-
-
 @ 58537364:705b4b85
2025-05-24 03:25:05
@ 58537364:705b4b85
2025-05-24 03:25:05Ep 228 "วิชาชีวิต"
คนเราเมื่อเกิดมาแล้ว ไม่ได้หวังแค่มีชีวิตรอดเท่านั้น แต่ยังปรารถนา "ความเจริญก้าวหน้า" และ "ความสุขในชีวิต"
จึงพากันศึกษาเล่าเรียนเพื่อให้มี "วิชาความรู้" สำหรับการประกอบอาชีพ โดยเชื่อว่า การงานที่มั่นคงย่อมนำ "ความสำเร็จ" และ "ความเจริญก้าวหน้า" มาให้
อย่างไรก็ตาม...ความสำเร็จในวิชาชีพหรือความเจริญก้าวหน้าในชีวิต ไม่ได้เป็นหลักประกันความสุขอย่างแท้จริง
แม้เงินทองและทรัพย์สมบัติจะช่วยให้ชีวิตมีความสุข สะดวก สบาย แต่ไม่ได้ช่วยให้สุขใจในสิ่งที่ตนมี หากยังรู้สึกว่า "ตนยังมีไม่พอ"
ขณะเดียวกันชื่อเสียงเกียรติยศที่ได้มาก็ไม่ช่วยให้คลายความทุกข์ใจ เมื่อต้องเผชิญปัญหาต่างๆ นาๆ
ทั้งการพลัดพราก การสูญเสียบุคคลผู้เป็นที่รัก ความเจ็บป่วย และความตายที่ต้องเกิดขึ้นกับทุกคน
ยิ่งกว่านั้น...ความสำเร็จในอาชีพและความเจริญก้าวหน้าในชีวิต ล้วนเป็น "สิ่งไม่เที่ยง" แปรผันตกต่ำ ไม่สามารถควบคุมได้
วิชาชีพทั้งหลายช่วยให้เราหาเงินได้มากขึ้น แต่ไม่ได้ช่วยให้เราเข้าถึง "ความสุขที่แท้จริง"
คนที่ประสบความสำเร็จในวิชาชีพไม่น้อย ที่มีชีวิตอมทุกข์ ความเครียดรุมเร้า สุขภาพเสื่อมโทรม
หากเราไม่อยากเผชิญกับสิ่งเหล่านี้ ควรเรียน "วิชาชีวิต" เพื่อเข้าใจโลก เข้าใจชีวิต รู้เท่าทันความผันแปรไปของสรรพสิ่ง
วิชาชีวิต...เรียนจากประสบการณ์ชีวิต เมื่อมีปัญหาต่างๆ ขอให้คิดว่า คือ "บททดสอบ"
จงหมั่นศึกษาหาบทเรียนจากวิชานี้อยู่เสมอ สร้าง "ความตระหนักรู้" ถึงความสำคัญในการมีชีวิต
ช่วงที่ผ่านมา เมื่อมีปัญหาฉันไม่สามารถหาทางออกจากทุกข์ได้เศร้า เสียใจ ทุรน ทุราย สอบตก "วิชาชีวิต"
โชคดีครูบาอาจารย์ให้ข้อคิด กล่าวว่า เป็นเรื่องธรรมดาหากเรายังไม่เข้าใจชีวิต ทุกสิ่งล้วนผันแปร เกิด-ดับ เป็นธรรมดา ท่านเมตตาส่งหนังสือเล่มนี้มาให้
เมื่อค่อยๆ ศึกษา ทำความเข้าใจ นำความทุกข์ที่เกิดขึ้นมาพิจารณา เห็นว่าเมื่อ "สอบตก" ก็ "สอบใหม่" จนกว่าจะผ่านไปได้
วิชาทางโลกเมื่อสอบตกยังเปิดโอกาสให้เรา "สอบซ่อม" วิชาทางธรรมก็เช่นเดียวกัน หากเจอปัญหา อุปสรรค หรือ ความทุกข์ถาโถมเข้ามา ขอให้เราตั้งสติ ว่า จะตั้งใจทำข้อสอบนี้ให้ผ่านไปให้จงได้
หากเราสามารถดำเนินชีวิตด้วยความเข้าใจ เราจะค้นพบ "วิชาชีวิต" ที่สามารถทำให้หลุดพ้นจากความทุกข์ได้แน่นอน
ด้วยรักและปรารถนาดี ปาริชาติ รักตะบุตร 21 เมษายน 2566
น้อมกราบขอบพระคุณพระ อ.ไพศาล วิสาโล เป็นอย่างสูง ที่ท่านเมตตา ให้ข้อธรรมะยามทุกข์ใจและส่งหนังสือมาให้ จึงตั้งใจอยากแบ่งปันเป็นธรรมทาน
-
 @ 2b998b04:86727e47
2025-05-24 03:16:38
@ 2b998b04:86727e47
2025-05-24 03:16:38Most of the assets I hold—real estate, equities, and businesses—depreciate in value over time. Some literally, like physical buildings and equipment. Some functionally, like tech platforms that age faster than they grow. Even cash, which should feel "safe," quietly loses ground to inflation. Yet I continue to build. I continue to hold. And I continue to believe that what I’m doing matters.
But underneath all of that — beneath the mortgages, margin trades, and business pivots — I’ve made a long-term bet:
Bitcoin will outlast the decay.
The Decaying System I Still Operate In
Let me be clear: I’m not a Bitcoin purist. I use debt. I borrow to acquire real estate. I trade with margin in a brokerage account. I understand leverage — not as a sin, but as a tool that must be used with precision and respect. But I’m also not naive.
The entire fiat-based financial system is built on a slow erosion of value. Inflation isn't a bug — it’s a feature. And it's why most business models, whether in real estate or retail, implicitly rely on asset inflation just to stay solvent.
That’s not sustainable. And it’s not honest.
The Bitcoin Thesis: Deflation That Works for You
Bitcoin is fundamentally different. Its supply is fixed. Its issuance is decreasing. Over time, as adoption grows and fiat weakens, Bitcoin’s purchasing power increases.
That changes the game.
If you can hold even a small portion of your balance sheet in BTC — not just as an investment, but as a strategic hedge — it becomes a way to offset the natural depreciation of your other holdings. Your buildings may age. Your cash flow may fluctuate. But your Bitcoin, if properly secured and held with conviction, becomes the anchor.
It’s not about day trading BTC or catching the next ATH. It’s about understanding that in a world designed to leak value, Bitcoin lets you patch the hole.
Why This Matters for Builders
If you run a business — especially one with real assets, recurring costs, or thin margins — you know how brutal depreciation can be. Taxes, maintenance, inflation, replacement cycles… it never stops.
Adding BTC to your long-term treasury isn’t about becoming a "crypto company." It’s about becoming anti-fragile. It’s about building with a component that doesn’t rot.
In 5, 10, or 20 years, I may still be paying off mortgages and navigating property cycles. But if my Bitcoin allocation is still intact, still growing in real purchasing power… then I haven’t just preserved wealth. I’ve preserved optionality. I’ve created a counterbalance to the relentless decay of everything else.
Final Word
I still play the fiat game — because for now, I have to. But I’m no longer betting everything on it. Bitcoin is my base layer now. Quiet, cold-stored, and uncompromising.
It offsets depreciation — not just financially, but philosophically. It reminds me that not everything has to erode. Not everything has to be sacrificed to time or policy or inflation.
Some things can actually hold. Some things can last.
And if I build right — maybe what I build can last too.
If this resonated, feel free to send a zap — it helps me keep writing and building from a place of conviction.
This article was co-written with the help of ChatGPT, a tool I use to refine and clarify what I’m working through in real time.
-
 @ 502ab02a:a2860397
2025-05-24 01:14:43
@ 502ab02a:a2860397
2025-05-24 01:14:43ในสายตาคนรักสุขภาพทั่วโลก “อโวคาโด” คือผลไม้ในฝัน มันมีไขมันดี มีไฟเบอร์สูง ช่วยลดคอเลสเตอรอลได้ มีวิตามินอี มีโพแทสเซียม และที่สำคัญคือ "ดูดี" ทุกครั้งที่ถูกปาดวางบนขนมปังโฮลวีตในชามสลัด หรือบนโฆษณาอาหารคลีนสุดหรู
แต่ในสายตาชาวไร่บางคนในเม็กซิโกหรือชุมชนพื้นเมืองในโดมินิกัน อโวคาโดไม่ใช่ผลไม้แห่งสุขภาพ แต่มันคือสัญลักษณ์ของความรุนแรง การกดขี่ และการสูญเสียเสรีภาพในผืนดินของตัวเอง
เมื่ออาหารกลายเป็นทองคำ กลุ่มอิทธิพลก็ไม่เคยพลาดจะเข้าครอบครอง
เรามักได้ยินคำว่า "ทองคำเขียว" หรือ Green Gold ใช้เรียกอโวคาโด เพราะในรอบ 20 ปีที่ผ่านมา ความต้องการบริโภคของมันพุ่งสูงขึ้นเป็นเท่าตัว โดยเฉพาะในสหรัฐฯ และยุโรป จากผลการวิจัยของมหาวิทยาลัยฮาร์วาร์ดและข้อมูลการส่งออกของ USDA พบว่า 90% ของอโวคาโดที่บริโภคในอเมริกา มาจากรัฐมิโชอากังของเม็กซิโก พื้นที่ซึ่งควบคุมโดยกลุ่มค้ายาเสพติดไม่ต่างจากเจ้าของสวนตัวจริง
พวกเขาเรียกเก็บ “ค่าคุ้มครอง” จากเกษตรกร โดยใช้วิธีเดียวกับมาเฟีย คือ ถ้าไม่จ่าย ก็เจ็บตัวหรือหายตัว ไม่ว่าจะเป็นกลุ่ม CJNG (Jalisco New Generation Cartel), Familia Michoacana หรือ Caballeros Templarios พวกเขาไม่ได้สนใจว่าใครปลูกหรือใครรดน้ำ ตราบใดที่ผลผลิตสามารถเปลี่ยนเป็นเงินได้
องค์กรอาชญากรรมเหล่านี้ไม่ได้แค่ “แฝงตัว” ในอุตสาหกรรม แต่ ยึดครอง ห่วงโซ่การผลิตทั้งหมด ตั้งแต่แปลงปลูกไปจนถึงโรงบรรจุและเส้นทางขนส่ง คนที่ไม่ยอมเข้าระบบมืดอาจต้องพบจุดจบในป่า หรือไม่มีชื่ออยู่ในทะเบียนบ้านอีกต่อไป
จากรายงานของเว็บไซต์ Food is Power องค์กรไม่แสวงกำไรด้านความยุติธรรมด้านอาหารในสหรัฐฯ เผยว่า ในปี 2020 มีเกษตรกรในเม็กซิโกจำนวนมากที่ถูกข่มขู่ บางรายถึงขั้นถูกฆาตกรรม เพราะปฏิเสธจ่ายค่าคุ้มครองจากกลุ่มค้ายา
การปลูกอโวคาโดไม่ใช่เรื่องเบาๆ กับธรรมชาติ เพราะมันต้องการ “น้ำ” มากถึง 272 ลิตรต่อผลเดียว! เรามาดูว่า “272 ลิตร” นี้ เท่ากับอะไรบ้างในชีวิตจริง อาบน้ำฝักบัวนาน 10–12 นาที (โดยเฉลี่ยใช้น้ำ 20–25 ลิตรต่อนาที) ใช้น้ำซักเสื้อผ้าเครื่องหนึ่ง (เครื่องซักผ้า 1 ครั้งกินประมาณ 60–100 ลิตร) น้ำดื่มของคนหนึ่งคนได้นานเกือบ เดือน (คนเราต้องการน้ำดื่มประมาณ 1.5–2 ลิตรต่อวัน)
ถ้าเราใช้ข้อมูลจาก FAO และ Water Footprint Network การผลิตเนื้อวัว 1 กิโลกรัม ต้องใช้น้ำ 15,000 ลิตร (รวมทั้งการปลูกหญ้า อาหารสัตว์ การดื่มน้ำของวัว ฯลฯ) ได้โปรตีนราว 250 กรัม อโวคาโด 1 กิโลกรัม (ราว 5 ผล) ใช้น้ำประมาณ 1,360 ลิตร ได้โปรตีนเพียง 6–8 กรัมเท่านั้น พูดง่ายๆคือ เมื่อเทียบอัตราส่วนเป็นลิตรต่อกรัมโปรตีนแล้วนั้น วัวใช้น้ำ 60 ลิตรต่อกรัมโปรตีน / อโวคาโด ใช้น้ำ 194 ลิตรต่อกรัมโปรตีน แถมการเลี้ยงวัวในระบบธรรมชาติ (เช่น pasture-raised หรือ regenerative farming) ยังสามารถเป็นส่วนหนึ่งของระบบหมุนเวียนน้ำและคาร์บอนได้ พอเห็นภาพแล้วใช่ไหมครับ ดังนั้นเราควรระมัดระวังการเสพสื่อเอาไว้ด้วยว่า คำว่า "ดีต่อโลก" ไม่ได้หมายถึงพืชอย่างเดียว ทุกธุรกิจถ้าทำแบบที่ควรทำ มันยังสามารถผลักดันโลกไม่ให้ตกอยู่ในมือองค์กร future food ได้ เพราะมูลค่ามันสูงมาก
และเมื่อราคาสูง พื้นที่เพาะปลูกก็ขยายอย่างไร้การควบคุม ป่าธรรมชาติในรัฐมิโชอากังถูกแอบโค่นแบบผิดกฎหมายเพื่อแปลงสภาพเป็นไร่ “ทองเขียว” ข้อมูลจาก Reuters พบว่าผลไม้ที่ถูกส่งออกไปยังสหรัฐฯ บางส่วนมาจากแปลงปลูกที่บุกรุกป่าคุ้มครอง และรัฐบาลเองก็ไม่สามารถควบคุมได้เพราะอิทธิพลของกลุ่มทุนและมาเฟีย
ในโดมินิกันก็เช่นกัน มีรายงานจากสำนักข่าว Gestalten ว่าพื้นที่ป่าสงวนหลายพันไร่ถูกเปลี่ยนเป็นไร่อโวคาโด เพื่อป้อนตลาดผู้บริโภคในอเมริกาและยุโรปโดยตรง โดยไม่มีการชดเชยใดๆ แก่ชุมชนท้องถิ่น
สุขภาพที่ดีไม่ควรได้มาจากการทำลายสุขภาพของคนอื่น ไม่ควรมีผลไม้ใดที่ดูดีในจานของเรา แล้วเบื้องหลังเต็มไปด้วยคราบเลือดและน้ำตาของคนปลูก
เฮียไม่ได้จะบอกให้เลิกกินอโวคาโดเลย แต่เฮียอยากให้เรารู้ทัน ว่าความนิยมของอาหารสุขภาพวันนี้ กำลังเป็นสนามใหม่ของกลุ่มทุนโลก ที่พร้อมจะครอบครองด้วย “อำนาจอ่อน” ผ่านแบรนด์อาหารธรรมชาติ ผ่านกฎหมายสิ่งแวดล้อม หรือแม้แต่การครอบงำตลาดเสรีด้วยกำลังอาวุธ
นี่ไม่ใช่เรื่องไกลตัว เพราะเมื่อกลุ่มทุนเริ่มฮุบเมล็ดพันธุ์ คุมเส้นทางขนส่ง คุมฉลาก Certified Organic ทั้งหลาย พวกเขาก็ “ควบคุมสุขภาพ” ของผู้บริโภคเมืองอย่างเราไปด้วยโดยอ้อม
คำถามสำคัญที่มาทุกครั้งเวลามีเนื้อหาอะไรมาฝากคือ แล้วเราจะทำอะไรได้? 555555 - เลือกบริโภคผลไม้จากแหล่งที่โปร่งใสหรือปลูกเองได้ - สนับสนุนเกษตรกรรายย่อยที่ไม่อยู่ภายใต้กลุ่มทุน - ใช้เสียงของผู้บริโภคกดดันให้มีระบบตรวจสอบต้นทางจริง ไม่ใช่แค่ฉลากเขียวสวยๆ - และที่สำคัญ อย่าเชื่อว่า “ทุกสิ่งที่เขาวางให้ดูสุขภาพดี” จะดีจริง (ข้อนี่ละตัวดีเลยครับ)
สุขภาพไม่ใช่สินค้า และอาหารไม่ควรเป็นอาวุธของกลุ่มทุน หากเราเริ่มตระหนักว่าอาหารคือการเมือง น้ำคืออำนาจ และแปลงเกษตรคือสนามรบ เฮียเชื่อว่าผู้บริโภคอย่างเราจะไม่ยอมเป็นหมากอีกต่อไป #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ b7274d28:c99628cb
2025-05-24 01:02:32
@ b7274d28:c99628cb
2025-05-24 01:02:32A few months ago, a nostrich was switching from iOS to Android and asked for suggestions for #Nostr apps to try out. nostr:npub18ams6ewn5aj2n3wt2qawzglx9mr4nzksxhvrdc4gzrecw7n5tvjqctp424 offered the following as his response:
nostr:nevent1qvzqqqqqqypzq0mhp4ja8fmy48zuk5p6uy37vtk8tx9dqdwcxm32sy8nsaa8gkeyqydhwumn8ghj7un9d3shjtnwdaehgunsd3jkyuewvdhk6tcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszythwden5te0dehhxarj9emkjmn99uqzpwwts6n28eyvjpcwvu5akkwu85eg92dpvgw7cgmpe4czdadqvnv984rl0z
Yes. #Android users are fortunate to have some powerful Nostr apps and tools at our disposal that simply have no comparison over on the iOS side. However, a tool is only as good as the knowledge of the user, who must have an understanding of how best to wield it for maximum effect. This fact was immediately evidenced by replies to Derek asking, "What is the use case for Citrine?" and "This is the first time I'm hearing about Citrine and Pokey. Can you give me links for those?"
Well, consider this tutorial your Nostr starter-kit for Android. We'll go over installing and setting up Amber, Amethyst, Citrine, and Pokey, and as a bonus we'll be throwing in the Zapstore and Coinos to boot. We will assume no previous experience with any of the above, so if you already know all about one or more of these apps, you can feel free to skip that tutorial.
So many apps...
You may be wondering, "Why do I need so many apps to use Nostr?" That's perfectly valid, and the honest answer is, you don't. You can absolutely just install a Nostr client from the Play Store, have it generate your Nostr identity for you, and stick with the default relays already set up in that app. You don't even need to connect a wallet, if you don't want to. However, you won't experience all that Nostr has to offer if that is as far as you go, any more than you would experience all that Italian cuisine has to offer if you only ever try spaghetti.
Nostr is not just one app that does one thing, like Facebook, Twitter, or TikTok. It is an entire ecosystem of applications that are all built on top of a protocol that allows them to be interoperable. This set of tools will help you make the most out of that interoperability, which you will never get from any of the big-tech social platforms. It will provide a solid foundation for you to build upon as you explore more and more of what Nostr has to offer.
So what do these apps do?

Fundamental to everything you do on Nostr is the need to cryptographically sign with your private key. If you aren't sure what that means, just imagine that you had to enter your password every time you hit the "like" button on Facebook, or every time you commented on the latest dank meme. That would get old really fast, right? That's effectively what Nostr requires, but on steroids.
To keep this from being something you manually have to do every 5 seconds when you post a note, react to someone else's note, or add a comment, Nostr apps can store your private key and use it to sign behind the scenes for you. This is very convenient, but it means you are trusting that app to not do anything with your private key that you don't want it to. You are also trusting it to not leak your private key, because anyone who gets their hands on it will be able to post as you, see your private messages, and effectively be you on Nostr. The more apps you give your private key to, the greater your risk that it will eventually be compromised.
Enter #Amber, an application that will store your private key in only one app, and all other compatible Nostr apps can communicate with it to request a signature, without giving any of those other apps access to your private key.
Most Nostr apps for Android now support logging in and signing with Amber, and you can even use it to log into apps on other devices, such as some of the web apps you use on your PC. It's an incredible tool given to us by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, and only available for Android users. Those on iPhone are incredibly jealous that they don't have anything comparable, yet.

Speaking of nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, the next app is also one of his making.
All Nostr data is stored on relays, which are very simple servers that Nostr apps read notes from and write notes to. In most forms of social media, it can be a pain to get your own data out to keep a backup. That's not the case on Nostr. Anyone can run their own relay, either for the sake of backing up their personal notes, or for others to post their notes to, as well.
Since Nostr notes take up very little space, you can actually run a relay on your phone. I have been on Nostr for almost 2 and a half years, and I have 25,000+ notes of various kinds on my relay, and a backup of that full database is just 24MB on my phone's storage.
Having that backup can save your bacon if you try out a new Nostr client and it doesn't find your existing follow list for some reason, so it writes a new one and you suddenly lose all of the people you were following. Just pop into your #Citrine relay, confirm it still has your correct follow list or import it from a recent backup, then have Citrine restore it. Done.
Additionally, there are things you may want to only save to a relay you control, such as draft messages that you aren't ready to post publicly, or eCash tokens, which can actually be saved to Nostr relays now. Citrine can also be used with Amber for signing into certain Nostr applications that use a relay to communicate with Amber.
If you are really adventurous, you can also expose Citrine over Tor to be used as an outbox relay, or used for peer-to-peer private messaging, but that is far more involved than the scope of this tutorial series.

You can't get far in Nostr without a solid and reliable client to interact with. #Amethyst is the client we will be using for this tutorial because there simply isn't another Android client that comes close, so far. Moreover, it can be a great client for new users to get started on, and yet it has a ton of features for power-users to take advantage of as well.
There are plenty of other good clients to check out over time, such as Coracle, YakiHonne, Voyage, Olas, Flotilla and others, but I keep coming back to Amethyst, and by the time you finish this tutorial, I think you'll see why. nostr:npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z and others who have contributed to Amethyst have really built something special in this client, and it just keeps improving with every update that's shipped.

Most social media apps have some form of push notifications, and some Nostr apps do, too. Where the issue comes in is that Nostr apps are all interoperable. If you have more than one application, you're going to have both of them notifying you. Nostr users are known for having five or more Nostr apps that they use regularly. If all of them had notifications turned on, it would be a nightmare. So maybe you limit it to only one of your Nostr apps having notifications turned on, but then you are pretty well locked-in to opening that particular app when you tap on the notification.
Pokey, by nostr:npub1v3tgrwwsv7c6xckyhm5dmluc05jxd4yeqhpxew87chn0kua0tjzqc6yvjh, solves this issue, allowing you to turn notifications off for all of your Nostr apps, and have Pokey handle them all for you. Then, when you tap on a Pokey notification, you can choose which Nostr app to open it in.
Pokey also gives you control over the types of things you want to be notified about. Maybe you don't care about reactions, and you just want to know about zaps, comments, and direct messages. Pokey has you covered. It even supports multiple accounts, so you can get notifications for all the npubs you control.

One of the most unique and incredibly fun aspects of Nostr is the ability to send and receive #zaps. Instead of merely giving someone a 👍️ when you like something they said, you can actually send them real value in the form of sats, small portions of a Bitcoin. There is nothing quite like the experience of receiving your first zap and realizing that someone valued what you said enough to send you a small amount (and sometimes not so small) of #Bitcoin, the best money mankind has ever known.
To be able to have that experience, though, you are going to need a wallet that can send and receive zaps, and preferably one that is easy to connect to Nostr applications. My current preference for that is Alby Hub, but not everyone wants to deal with all that comes along with running a #Lightning node. That being the case, I have opted to use nostr:npub1h2qfjpnxau9k7ja9qkf50043xfpfy8j5v60xsqryef64y44puwnq28w8ch for this tutorial, because they offer one of the easiest wallets to set up, and it connects to most Nostr apps by just copy/pasting a connection string from the settings in the wallet into the settings in your Nostr app of choice.
Additionally, even though #Coinos is a custodial wallet, you can have it automatically transfer any #sats over a specified threshold to a separate wallet, allowing you to mitigate the custodial risk without needing to keep an eye on your balance and make the transfer manually.

Most of us on Android are used to getting all of our mobile apps from one souce: the Google Play Store. That's not possible for this tutorial series. Only one of the apps mentioned above is available in Google's permissioned playground. However, on Android we have the advantage of being able to install whatever we want on our device, just by popping into our settings and flipping a toggle. Indeed, thumbing our noses at big-tech is at the heart of the Nostr ethos, so why would we make ourselves beholden to Google for installing Nostr apps?
The nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8 is an alternative app store made by nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9 as a resource for all sorts of open-source apps, but especially Nostr apps. What is more, you can log in with Amber, connect a wallet like Coinos, and support the developers of your favorite Nostr apps directly within the #Zapstore by zapping their app releases.
One of the biggest features of the Zapstore is the fact that developers can cryptographically sign their app releases using their Nostr keys, so you know that the app you are downloading is the one they actually released and hasn't been altered in any way. The Zapstore will warn you and won't let you install the app if the signature is invalid.
Getting Started
Since the Zapstore will be the source we use for installing most of the other apps mentioned, we will start with installing the Zapstore.
We will then use the Zapstore to install Amber and set it up with our Nostr account, either by creating a new private key, or by importing one we already have. We'll also use it to log into the Zapstore.
Next, we will install Amethyst from the Zapstore and log into it via Amber.
After this, we will install Citrine from the Zapstore and add it as a local relay on Amethyst.
Because we want to be able to send and receive zaps, we will set up a wallet with CoinOS and connect it to Amethyst and the Zapstore using Nostr Wallet Connect.
Finally, we will install Pokey using the Zapstore, log into it using Amber, and set up the notifications we want to receive.
By the time you are done with this series, you will have a great head-start on your Nostr journey compared to muddling through it all on your own. Moreover, you will have developed a familiarity with how things generally work on Nostr that can be applied to other apps you try out in the future.
Continue to Part 2: Installing the Zapstore. (Coming Soon)
-
 @ 90152b7f:04e57401
2025-05-23 23:38:49
@ 90152b7f:04e57401
2025-05-23 23:38:49WikiLeaks The Global Intelligence Files
Released on 2013-03-04 00:00 GMT
| Email-ID | 296467 | | -------- | -------------------------- | | Date | 2007-10-29 20:54:22 | | From | <hrwpress@hrw.org> | | To | <responses@stratfor.com> |
Gaza: Israel's Fuel and Power Cuts Violate Laws of War\ \ For Immediate Release\ \ Gaza: Israel's Fuel and Power Cuts Violate Laws of War\ \ Civilians Should Not Be Penalized for Rocket Attacks by Armed Groups\ \ (New York, October 29, 2007) - Israel's decision to limit fuel and\ electricity to the Gaza Strip in retaliation for unlawful rocket attacks\ by armed groups amounts to collective punishment against the civilian\ population of Gaza, in violation of international law, and will worsen the\ humanitarian crisis there, Human Rights Watch said today.\ \ "Israel may respond to rocket attacks by armed groups to protect its\ population, but only in lawful ways," said Sarah Leah Whitson, director of\ Human Rights Watch's Middle East division. "Because Israel remains an\ occupying power, in light of its continuing restrictions on Gaza, Israel\ must not take measures that harm the civilian population - yet that is\ precisely what cutting fuel or electricity for even short periods will\ do."\ \ On Sunday, the Israeli Defense Ministry ordered the reduction of fuel\ shipments from Israel to Gaza. A government spokesman said the plan was to\ cut the amount of fuel by 5 to 11 percent without affecting the supply of\ industrial fuel for Gaza's only power plant.\ \ According to Palestinian officials, fuel shipments into Gaza yesterday\ fell by more than 30 percent.\ \ In response to the government's decision, a group of 10 Palestinian and\ Israeli human rights groups petitioned the Israeli Supreme Court on\ Sunday, seeking an immediate injunction against the fuel and electricity\ cuts. The court gave the government five days to respond but did not issue\ a temporary injunction. On Monday, the groups requested an urgent hearing\ before the five days expire.\ \ Last Thursday, Defense Minister Ehud Barak approved cutting electricity to\ Gaza for increasing periods in response to ongoing rocket attacks against\ civilian areas in Israel, but the government has not yet implemented the\ order.\ \ The rockets fired by Palestinian armed groups violate the international\ legal prohibition on indiscriminate attacks because they are highly\ inaccurate and cannot be directed at a specific target. Because Hamas\ exercises power inside Gaza, it is responsible for stopping indiscriminate\ attacks even when carried out by other groups, Human Rights Watch said.\ \ On Friday, Israeli Prime Minister Ehud Olmert said that Israel would\ respond strongly to the ongoing attacks without allowing a humanitarian\ crisis. But the UN's top humanitarian official, UN Deputy\ Secretary-General John Holmes, said that a "serious humanitarian crisis"\ in Gaza already exists, and called on Israel to lift the economic blockade\ that it tightened after Hamas seized power in June.\ \ Israel's decision to cut fuel and electricity is the latest move aimed\ ostensibly against Hamas that is affecting the entire population of Gaza.\ In September, the Israeli cabinet declared Gaza "hostile territory" and\ voted to "restrict the passage of various goods to the Gaza Strip and\ reduce the supply of fuel and electricity." Since then, Israel has\ increasingly blocked supplies into Gaza, letting in limited amounts of\ essential foodstuffs, medicine and humanitarian supplies. According to\ Holmes, the number of humanitarian convoys entering Gaza had dropped to\ 1,500 in September from 3,000 in July.\ \ "Cutting fuel and electricity obstructs vital services," Whitson said.\ "Operating rooms, sewage pumps, and water well pumps all need electricity\ to run."\ \ Israel sells to Gaza roughly 60 percent of the electricity consumed by the\ territory's 1.5 million inhabitants. In June 2006, six Israeli missiles\ struck Gaza's only power plant; today, for most residents, electricity is\ available during only limited hours.\ \ Israeli officials said they would cut electricity for 15 minutes after\ each rocket attack and then for increasingly longer periods if the attacks\ persist. Deputy Defense Minister Matan Vilnai said Israel would\ "dramatically reduce" the power it supplied to Gaza over a period of\ weeks.\ \ Cutting fuel or electricity to the civilian population violates a basic\ principle of international humanitarian law, or the laws of war, which\ prohibit a government that has effective control over a territory from\ attacking or withholding objects that are essential to the survival of the\ civilian population. Such an act would also violate Israel's duty as an\ occupying power to safeguard the health and welfare of the population\ under occupation.\ \ Israel withdrew its military forces and settlers from the Gaza Strip in\ 2005. Nonetheless, Israel remains responsible for ensuring the well-being\ of Gaza's population for as long as, and to the extent that, it retains\ effective control over the area. Israel still exercises control over\ Gaza's airspace, sea space and land borders, as well as its electricity,\ water, sewage and telecommunications networks and population registry.\ Israel can and has also reentered Gaza for security operations at will.\ \ Israeli officials state that by declaring Gaza "hostile territory," it is\ no longer obliged under international law to supply utilities to the\ civilian population, but that is a misstatement of the law.\ \ "A mere declaration does not change the facts on the ground that impose on\ Israel the status and obligations of an occupying power," said Whitson.\ \ For more information, please contact:\ \ In New York, Fred Abrahams (English, German): +1-917-385-7333 (mobile)\ \ In Washington, DC, Joe Stork (English): +1-202-299-4925 (mobile)\ \ In Cairo, Gasser Abdel-Razek (Arabic, English): +20-2-2-794-5036 (mobile);\ or +20-10-502-9999 (mobile)
-
 @ 34f1ddab:2ca0cf7c
2025-05-23 23:15:14
@ 34f1ddab:2ca0cf7c
2025-05-23 23:15:14Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 6c05c73e:c4356f17
2025-05-23 22:59:35
@ 6c05c73e:c4356f17
2025-05-23 22:59:35Como a grande maioria dos brasileiros. Eu não comecei um negócio porque “queria empreender”. Diferente disso, eu PRECISAVA para poder pagar contas e manter o básico.
Festas, openbar e camisas
Meu primeiro negócio foi na verdade um combo. Eu tinha saído do último trampo e eu gostava de festas. Então, comecei a organizar uma festa mensalmente na casa do meu pai. Eu pagava a água, energia e dava uma grana para ele. Em troca, organizava festa de sábado para domingo open bar.
A fórmula era simples. Criava o evento da festa no facebook, convidava todo mundo que conhecia. Panfletava na cidade e espalhava cartazes nos pontos de ônibus sobre a festa. E, para fechar com chave de ouro. Mulher era OFF até 20:00. Consequência? Os caras vinham e pagavam o ingresso deles e delas. Kkkkk. E, enchia…
Comecei a notar que a galera se vestia mal. E, pensei: "Porque não vestir eles?” Pimba! Comecei a desenha e confeccionar camisas para vender nas festas. E, pimba denovo! Vendeu, tudo! Fiz 2 coleções e mais algumas festas. Até o dia que um menino deu PT de tanto beber e decidi que era hora de tentar outra coisa.
Como assim a Apple não vai vender mais os carregadores?
Isso, foi durante a pandemia. A Apple decidiu vender o telefone e o cabo. E, você que lute com a fonte. Estava difícil achar dinheiro no mercado naqueles tempos e eu pensei. Vou pesquisar no google trends e validar a ideia. Caixa! Tinha mais de 80 pts de busca. Colei em SP, no Brás e comprei literalmente. Todo meu dinheiro de cabo de iphone, carregador e bateria portátil.
Fiquei com R$100 na conta. Para fazer um lanche e pagar pelo uber para voltar para casa. Chegando aqui, eu tirei foto e fiz várias copys. Anunciei no Olx, Mercado Livre e Facebook. Impulsionei os anúncios no OLX, vendi para familiares e amigos, e; vendia até para quem estava na rua. Fiz entrega de bike, a pé, de ônibus e é isso mesmo. Tem que ralar. Para queimar o resto da mercadoria. Deixei com uma loja de eletrônicos e fiz consignado. E, hora da próxima ideia.
Mulheres, doces e TPM
Meu penúltimo negócio veio depois dos cabos. Eu pesquisei na net, negócios online para começar com pouca grana. (Depois que paguei as contas do dia a dia, sobraram R$3mil). E, achei uma pesquisa mostrando que doces. Tinha baixa barreira de entrada e exigia poucos equipamentos. Eu trabalhei em restaurante por muitos anos e sabia como lucrar com aquilo. Além do mais, mulheres consomem mais doce em uma certa época do mês.
Não deu outra, convidei 2 pessoas para serem sócias. Desenvolvemos os produtos, fotografamos e fizemos as copys. Em sequência, precisávamos vender. Então, lá vamos denovo: Ifood, WPP, 99food (na época), Uber eats (na época), Elo7, famílias e amigos e; por fim começamos a vender consignado com alguns restaurantes e lojas. Foi uma época em que aprendi a prospectar clientes de todas as maneiras possíveis.
De novo, minha maior dificuldade era a locomoção para fazer entregas. Só tinha uma bike. Mas, entregávamos. Os primeiros 3 meses foram difíceis demais. Mas, rolou. No fim, nossas maiores vendas vinham de: Ifood, encomendas de festas e consignados. Mas, como nem tudo são flores. Meus dois sócios tomaram outros caminhos e abandonaram o projeto. Galera, está tudo bem com isso. Isso acontece o tempo todo. A vida muda e temos que aprender a aceitar isso. Vida que segue e fui para frente de novo.
Sobre paixões, paciência e acreditar
Estava eu comemorando meu níver de 30 anos, num misto de realizações e pouco realizado. Como assim? Sabe quando você faz um monte de coisas, mas ainda assim. Não sente que é aquilo? Pois então…
Eu amo investimentos, livros, escrever e sempre curti trocar ideia com amigos e família sobre como se desenvolver. Desde que comecei a usar a internet eu criei: Canal no youtube, páginas no IG e FB, pinterest, steemit, blog e até canal no Telegram. Mas, nunca tinha consistente sabe? Tipo assim, vou fazer isso por um ano e plantar 100 sementes aqui. Enfim, inconsistência te derruba meu amigo…Eu voltei a trabalhar com restaurantes e estava doido para mudar de área. Estava exausto de trabalhar e meu wpp não parava de tocar. Fui estudar ADM e Desenvolvimento de sistemas no Senac. Dois anos depois, formei. Consegui trabalho.
E, comecei a pensar em como criar um negócio online, escalável e multilíngue. Passei os próximos 7 meses desenhando e pensando como. Mas, tinha que dar o primeiro passo. Criei um site e fui escrevendo textos. Os primeiros 30 foram aquilo, os próximos 10 melhoraram muito e os 10 a seguir eu fiquei bem satisfeitos. Hoje, tenho o negócio que estava na cabeça desde 2023. Mas, olha o tamanho da volta que o universo me fez dar e aprender para chegar aqui hoje. Dicas? Só 3:
- Você precisa usar a internet para fazer negócio. Em todos os negócios que falei, sempre teve algo online. Não negligencie isso.
- Tem que aprender a vender e se vender.
- Confia em si mesmo e faz sem medo de errar. Porque, advinha? Você vai errar! Mas, vai aprender e melhorar. Tem que persistir…
Por hoje é isso. Tamo junto!
-
 @ bf47c19e:c3d2573b
2025-05-23 22:14:37
@ bf47c19e:c3d2573b
2025-05-23 22:14:37Originalni tekst na antenam.net
22.05.2025 / Autor: Ana Nives Radović
Da nema besplatnog ručka sigurno ste čuli svaki put kad bi neko poželio da naglasi da se sve na neki način plaća, iako možda tu cijenu ne primjećujemo odmah. Međutim, kada govorimo o događaju od kojeg je prošlo tačno 15 godina onda o „ručku“ ne govorimo u prenešenom smislu, već o porudžbini pice čija tržišna vrijednost iz godine u godinu dostiže iznos koji je čini najskupljom hranom koja je ikad poručena.
Tog 22. maja 2010. godine čovjek sa Floride pod imenom Laslo Hanjec potrošio je 10.000 bitcoina na dvije velike pice. U to vrijeme, ta količina bitcoina imala je tržišnu vrijednost od oko 41 dolar. Ako uzmemo u obzir da je vrijednost jedne jedinice ove digitalne valute danas nešto više od 111.000 dolara, tih 10.000 bitcoina danas bi značilo vrijednost od 1,11 milijardi dolara.
Nesvakidašnji događaj u digitalnoj i ugostiteljskoj istoriji, nastao zbog znatiželje poručioca koji je želio da se uvjeri da koristeći bitcoin može da plati nešto u stvarnom svijetu, pretvorio se u Bitcoin Pizza Day, kao podsjetnik na trenutak koji je označio prelaz bitcoina iz apstraktnog kriptografskog eksperimenta u nešto što ima stvarnu vrijednost.
Hanjec je bio znatiželjan i pitao se da li se prva, a u to vrijeme i jedina kriptovaluta može iskoristiti za kupovinu nečeg opipljivog. Objavio je ponudu na jednom forumu koja je glasila: 10.000 BTC za dvije pice. Jedan entuzijasta se javio, naručio pice iz restorana Papa John’s i ispisao zanimljivu stranicu istorije digitalne imovine.
Taj inicijalni zabilježeni finansijski dogovor dao je bitcoinu prvu široko prihvaćenu tržišnu vrijednost: 10.000 BTC za 41 dolar, čime je bitcoin napravio svoj prvi korak ka onome što danas mnogi zovu digitalnim zlatom.
Šta je zapravo bitcoin?
Bitcoin je oblik digitalnog novca koji je osmišljen da bude decentralizovan, transparentan i otporan na uticaj centralnih banaka. Kreirao ga je 2009. godine anonimni autor poznat kao Satoši Nakamoto, neposredno nakon globalne finansijske krize 2008. godine. U svojoj suštini, bitcoin je protokol, skup pravila koja sprovodi kompjuterski kod, koji omogućava korisnicima da bez posrednika sigurno razmjenjuju vrijednost putem interneta.
Osnova cijelog sistema je blockchain, distribuisana digitalna knjiga koju održavaju hiljade nezavisnih računara (tzv. čvorova) širom svijeta. Svaka transakcija se bilježi u novi „blok“, koji se potom dodaje u lanac (otud naziv „lanac blokova“, odnosno blockchain). Informacija koja se jednom upiše u blok ne može da se izbriše, niti promijeni, što omogućava više transparentnosti i više povjerenja.
Da bi blockchain mreža u kojoj se sve to odvija zadržala to svojstvo, bitcoin koristi mehanizam konsenzusa nazvan dokaz rada (proof-of-work), što znači da specijalizovani računari koji „rudare“ bitcoin rješavaju kompleksne matematičke probleme kako bi omogućili obavljanje transakcija i pouzdanost mreže.
Deflatorna priroda bitcoina
Najjednostavniji način da se razumije deflatorna priroda bitcoina je da pogledamo cijene izražene u valuti kojoj plaćamo. Sigurno ste u posljednje vrijeme uhvatili sebe da komentarišete da ono što je prije nekoliko godina koštalo 10 eura danas košta 15 ili više. Budući da to ne zapažate kada je u pitanju cijena samo određenog proizvoda ili usluge, već kao sveprisutan trend, shvatate da se radi o tome da je novac izgubio vrijednost. Na primjer, kada je riječ o euru, otkako je Evropska centralna banka počela intenzivno da doštampava novac svake godine, pa je od 2009. kada je program tzv. „kvantitativnog popuštanja“ započet euro zabilježio kumulativnu inflaciju od 42,09% zbog povećane količine sredstava u opticaju.
Međutim, kada je riječ o bitcoinu, njega nikada neće biti više od 21 milion koliko je izdato prvog dana, a to nepromjenjivo pravilo zapisano je i u njegovom kodu. Ova ograničena ponuda oštro se suprotstavlja principima koji važe kod monetarnih institucija, poput centralnih banaka, koje doštampavaju novac, često da bi povećale količinu u opticaju i tako podstakle finansijske tokove, iako novac zbog toga gubi vrijednost. Nasuprot tome, bitcoin se zadržava na iznosu od 21 milion, pa je upravo ta konačnost osnova za njegovu deflatornu prirodu i mogućnost da vremenom dobija na vrijednosti.
Naravno, ovo ne znači da je cijena bitcoina predodređena da samo raste. Ona je zapravo prilično volatilna i oscilacije su česte, posebno ukoliko, na primjer, posmatramo odnos cijena unutar jedne godine ili nekoliko mjeseci, međutim, gledano sa vremenske distance od četiri do pet godina bilo koji uporedni period od nastanka bitcoina do danas upućuje na to da je cijena u međuvremenu porasla. Taj trend će se nastaviti, tako da, kao ni kada je riječ o drugim sredstvima, poput zlata ili nafte, nema mjesta konstatacijama da je „vrijeme niskih cijena prošlo“.
Šta zapravo znači ovaj dan?
Bitcoin Pizza Day je za mnoge prilika da saznaju ponešto novo o bitcoinu, jer tada imaju priliku da o njemu čuju detalje sa raznih strana, jer kako se ovaj događaj popularizuje stvaraju se i nove prilike za učenje. Takođe, ovaj dan od 2021. obilježavaju picerije širom svijeta, u više od 400 gradova iz najmanje 75 zemalja, jer je za mnoge ovo prilika da korisnike bitcoina navedu da potroše djelić svoje imovine na nešto iz njihove ponude. Naravno, taj iznos je danasd zanemarljivo mali, a cijena jedne pice danas je otprilike 0,00021 bitcoina.
No, dok picerije širom svijeta danas na zabavan način pokušavaju da dođu do novih gostiju, ovaj dan je za mnoge vlasnike bitcoina nešto poput opomene da svoje digitalne novčiće ipak ne treba trošiti na nešto potrošno, jer je budućnost nepredvidiva. Bitcoin Pizza Day je dan kada se ideja pretvorila u valutu, kada su linije koda postale sredstvo razmjene.
Prvi let avionom trajao je svega 12 sekundi, a u poređenju sa današnjim transkontinentalnim linijama to djeluje gotovo neuporedivo i čudno, međutim, od nečega je moralo početi. Porudžbina pice plaćene bitcoinom označile su početak razmjene ove vrste, dok se, na primjer, tokom jučerašnjeg dana obim plaćanja bitcoinom premašio 23 milijarde dolara. Nauka i tehnologija nas podsjećaju na to da sve počinje malim, zanemarivim koracima.
-
 @ bf47c19e:c3d2573b
2025-05-23 21:54:43
@ bf47c19e:c3d2573b
2025-05-23 21:54:43Srpski prevod knjige "The Little Bitcoin Book"
Zašto je Bitkoin bitan za vašu slobodu, finansije i budućnost?
Verovatno ste čuli za Bitkoin u vestima ili da o njemu raspravljaju vaši prijatelji ili kolege. Kako to da se cena stalno menja? Da li je Bitkoin dobra investicija? Kako to uopšte ima vrednost? Zašto ljudi stalno govore o tome kao da će promeniti svet?
"Mala knjiga o Bitkoinu" govori o tome šta nije u redu sa današnjim novcem i zašto je Bitkoin izmišljen da obezbedi alternativu trenutnom sistemu. Jednostavnim rečima opisuje šta je Bitkoin, kako funkcioniše, zašto je vredan i kako utiče na individualnu slobodu i mogućnosti ljudi svuda - od Nigerije preko Filipina do Venecuele do Sjedinjenih Država. Ova knjiga takođe uključuje odeljak "Pitanja i odgovori" sa nekim od najčešće postavljanih pitanja o Bitkoinu.
Ako želite da saznate više o ovom novom obliku novca koji i dalje izaziva interesovanje i usvajanje širom sveta, onda je ova knjiga za vas.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:53:16
@ 6d5c826a:4b27b659
2025-05-23 21:53:16- DefGuard - True enterprise WireGuard with MFA/2FA and SSO. (Source Code)
Apache-2.0Rust - Dockovpn - Out-of-the-box stateless dockerized OpenVPN server which starts in less than 2 seconds. (Source Code)
GPL-2.0Docker - Firezone - WireGuard based VPN Server and Firewall. (Source Code)
Apache-2.0Docker - Gluetun VPN client - VPN client in a thin Docker container for multiple VPN providers, written in Go, and using OpenVPN or Wireguard, DNS over TLS, with a few proxy servers built-in.
MITdocker - Headscale - Self-hostable fork of Tailscale, cross-platform clients, simple to use, built-in (currently experimental) monitoring tools.
BSD-3-ClauseGo - Nebula - A scalable p2p VPN with a focus on performance, simplicity and security.
MITGo - ocserv - Cisco AnyConnect-compatible VPN server. (Source Code)
GPL-2.0C - OpenVPN - Uses a custom security protocol that utilizes SSL/TLS for key exchange. (Source Code)
GPL-2.0C - SoftEther - Multi-protocol software VPN with advanced features. (Source Code)
Apache-2.0C - sshuttle - Poor man's VPN.
LGPL-2.1Python - strongSwan - Complete IPsec implementation for Linux. (Source Code)
GPL-2.0C - WireGuard - Very fast VPN based on elliptic curve and public key crypto. (Source Code)
GPL-2.0C
- DefGuard - True enterprise WireGuard with MFA/2FA and SSO. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:52:59
@ 6d5c826a:4b27b659
2025-05-23 21:52:59- Ganeti - Cluster virtual server management software tool built on top of KVM and Xen. (Source Code)
BSD-2-ClausePython/Haskell - KVM - Linux kernel virtualization infrastructure. (Source Code)
GPL-2.0/LGPL-2.0C - OpenNebula - Build and manage enterprise clouds for virtualized services, containerized applications and serverless computing. (Source Code)
Apache-2.0C++ - oVirt - Manages virtual machines, storage and virtual networks. (Source Code)
Apache-2.0Java - Packer - A tool for creating identical machine images for multiple platforms from a single source configuration. (Source Code)
MPL-2.0Go - Proxmox VE - Virtualization management solution. (Source Code)
GPL-2.0Perl/Shell - QEMU - QEMU is a generic machine emulator and virtualizer. (Source Code)
LGPL-2.1C - Vagrant - Tool for building complete development environments. (Source Code)
BUSL-1.1Ruby - VirtualBox - Virtualization product from Oracle Corporation. (Source Code)
GPL-3.0/CDDL-1.0C++ - XCP-ng - Virtualization platform based on Xen Source and Citrix® Hypervisor (formerly XenServer). (Source Code)
GPL-2.0C - Xen - Virtual machine monitor for 32/64 bit Intel / AMD (IA 64) and PowerPC 970 architectures. (Source Code)
GPL-2.0C
- Ganeti - Cluster virtual server management software tool built on top of KVM and Xen. (Source Code)
-
 @ 611021ea:089a7d0f
2025-05-24 00:00:04
@ 611021ea:089a7d0f
2025-05-24 00:00:04The world of health and fitness data is booming. Users are tracking more aspects of their well-being than ever before, from daily steps and workout intensity to sleep patterns and caloric intake. But for developers looking to build innovative applications on this data, significant hurdles remain: ensuring user privacy, achieving interoperability between different services, and simply managing the complexity of diverse health metrics.
Enter the NIP-101h Health Profile Framework and its companion tools: the HealthNote SDK and the HealthNote API. This ecosystem is designed to empower developers to create next-generation health and fitness applications that are both powerful and privacy-preserving, built on the decentralized and user-centric principles of Nostr.
NIP-101h: A Standardized Language for Health Metrics
At the core of this ecosystem is NIP-101h. It's a Nostr Improvement Proposal that defines a standardized way to represent, store, and share granular health and fitness data. Instead of proprietary data silos, NIP-101h introduces specific Nostr event kinds for individual metrics like weight (kind
1351), height (kind1352), step count (kind1359), and many more.Key features of NIP-101h:
- Granularity: Each piece of health information (e.g., weight, caloric intake) is a distinct Nostr event, allowing for fine-grained control and access.
- User Control: Built on Nostr, the data remains under user control. Users decide what to share, with whom, and on which relays.
- Standardization: Defines common structures for units, timestamps, and metadata, promoting interoperability.
- Extensibility: New metrics can be added as new NIP-101h.X specifications, allowing the framework to evolve.
- Privacy by Design: Encourages the use of NIP-04/NIP-44 for encryption and includes a
consenttag for users to specify data-sharing preferences.
You can explore the full NIP-101h specification and its metric directory in the main project repository.
The HealthNote SDK: Simplifying Client-Side Integration
While NIP-101h provides the "what," the HealthNote SDK provides the "how" for client-side applications. This (currently draft) TypeScript SDK aims to make it trivial for developers to:
- Create & Validate NIP-101h Events: Easily construct well-formed Nostr events for any supported health metric, ensuring they conform to the NIP-101h specification.
- Handle Encryption: Seamlessly integrate with NIP-44 to encrypt sensitive health data before publication.
- Manage Consent: Automatically include appropriate
consenttags (e.g., defaulting toaggregate-only) to respect user preferences. - Publish to Relays: Interact with Nostr relays to publish the user's health data.
- Prepare Data for Analytics: Extract minimal, privacy-preserving "stat-blobs" for use with the HealthNote API.
The SDK's goal is to abstract away the low-level details of Nostr event creation and NIP-101h formatting, letting developers focus on their application's unique features.
The HealthNote API: Powerful Insights, Zero Raw Data Exposure
This is where things get really exciting for developers wanting to build data-driven features. The HealthNote API (detailed in
HealthNote-API.md) is a server-side component designed to provide powerful analytics over aggregated NIP-101h data without ever accessing or exposing individual users' raw, unencrypted metrics.Here's how it achieves this:
- Privacy-Preserving Ingestion: The SDK sends only "stat-blobs" to the API. These blobs contain the numeric value, unit, timestamp, and metric kind, but not the original encrypted content or sensitive user identifiers beyond what's necessary for aggregation.
- Aggregation at its Core: The API's endpoints are designed to return only aggregated data.
GET /trend: Provides time-series data (e.g., average daily step count over the last month).GET /correlate: Computes statistical correlations between two metrics (e.g., does increased activity duration correlate with changes in workout intensity?).GET /distribution: Shows how values for a metric are distributed across the user base.
- Built-in Privacy Techniques:
- k-Anonymity: Ensures that each data point in an aggregated response represents at least 'k' (e.g., 5) distinct users, preventing re-identification.
- Differential Privacy (Optional): Can add statistical noise to query results, further protecting individual data points while preserving overall trends.
- No Raw Data Access for Developers: Developers querying the API receive only these aggregated, anonymized results, perfect for powering charts, dashboards, and trend analysis in their applications.
A Typical Workflow
- A user records a workout in their NIP-101h-compatible fitness app.
- The app uses the HealthNote SDK to create NIP-101h events for metrics like distance, duration, and calories burned. Sensitive data is encrypted.
- The SDK publishes these events to the user's configured Nostr relays.
- The SDK also extracts stat-blobs (e.g.,
{ kind: 1363, value: 5, unit: 'km', ... }) and sends them to the HealthNote API for ingestion, tagged with anaggregate-onlyconsent. - Later, the app (or an authorized third-party service) queries the HealthNote API:
GET /trend?kind=1363&bucket=week&stat=sum. - The API returns a JSON object like:
{"series": [{"date": "2024-W20", "value": 15000}, ...]}showing the total distance run by all consenting users, week by week. This data can directly populate a trend chart.
Benefits for the Ecosystem
- For Users:
- Greater control and ownership of their health data.
- Ability to use a diverse range of interoperable health and fitness apps.
- Confidence that their data can contribute to insights without sacrificing personal privacy.
- For Developers:
- Easier to build sophisticated health and fitness applications without becoming privacy experts or building complex data aggregation pipelines.
- Access to rich, aggregated data for creating compelling user-facing features (trends, benchmarks, correlations).
- Reduced burden of storing and securing sensitive raw health data for analytical purposes.
- Opportunity to participate in an open, interoperable ecosystem.
The Road Ahead
The NIP-101h framework, the HealthNote SDK, and the HealthNote API are foundational pieces for a new generation of health and fitness applications. As these tools mature and gain adoption, we envision a vibrant ecosystem where users can seamlessly move their data between services, and developers can innovate rapidly, all while upholding the highest standards of privacy and user control.
We encourage developers to explore the NIP-101h specifications, experiment with the (upcoming) SDK, and review the HealthNote API design. Your feedback and contributions will be invaluable as we build this privacy-first future for health data.
https://github.com/HealthNoteLabs
-
 @ 6d5c826a:4b27b659
2025-05-23 21:52:43
@ 6d5c826a:4b27b659
2025-05-23 21:52:43- Darcs - Cross-platform version control system, like git, mercurial or svn but with a very different approach: focus on changes rather than snapshots. (Source Code)
GPL-2.0Haskell - Fossil - Distributed version control with built-in wiki and bug tracking. (Source Code)
BSD-2-ClauseC - Git - Distributed revision control and source code management (SCM) with an emphasis on speed. (Source Code)
GPL-2.0C - Mercurial - Distributed source control management tool. (Source Code)
GPL-2.0Python/C/Rust - Subversion - Client-server revision control system. (Source Code)
Apache-2.0C
- Darcs - Cross-platform version control system, like git, mercurial or svn but with a very different approach: focus on changes rather than snapshots. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:52:26
@ 6d5c826a:4b27b659
2025-05-23 21:52:26- grml - Bootable Debian Live CD with powerful CLI tools. (Source Code)
GPL-3.0Shell - mitmproxy - A Python tool used for intercepting, viewing and modifying network traffic. Invaluable in troubleshooting certain problems. (Source Code)
MITPython - mtr - Network utility that combines traceroute and ping. (Source Code)
GPL-2.0C - Sysdig - Capture system state and activity from a running Linux instance, then save, filter and analyze. (Source Code)
Apache-2.0Docker/Lua/C - Wireshark - The world's foremost network protocol analyzer. (Source Code)
GPL-2.0C
- grml - Bootable Debian Live CD with powerful CLI tools. (Source Code)
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-23 23:37:17
@ 5d4b6c8d:8a1c1ee3
2025-05-23 23:37:17@grayruby loves to blow up the odds of various sports markets at Predyx. Well, the jig is up, because I finally managed to deposit some sats at BetPlay where I can leverage the mismatched odds.
So, I've now locked in guaranteed wins on the 49ers winning the Super Bowl and the Panthers winning the Stanley Cup.
https://stacker.news/items/987847
-
 @ dfa02707:41ca50e3
2025-05-24 05:00:57
@ dfa02707:41ca50e3
2025-05-24 05:00:57
Good morning (good night?)! The No Bullshit Bitcoin news feed is now available on Moody's Dashboard! A huge shoutout to sir Clark Moody for integrating our feed.
Headlines
- Spiral welcomes Ben Carman. The developer will work on the LDK server and a new SDK designed to simplify the onboarding process for new self-custodial Bitcoin users.
- The Bitcoin Dev Kit Foundation announced new corporate members for 2025, including AnchorWatch, CleanSpark, and Proton Foundation. The annual dues from these corporate members fund the small team of open-source developers responsible for maintaining the core BDK libraries and related free and open-source software (FOSS) projects.
- Strategy increases Bitcoin holdings to 538,200 BTC. In the latest purchase, the company has spent more than $555M to buy 6,556 coins through proceeds of two at-the-market stock offering programs.
- Spar supermarket experiments with Bitcoin payments in Zug, Switzerland. The store has introduced a new payment method powered by the Lightning Network. The implementation was facilitated by DFX Swiss, a service that supports seamless conversions between bitcoin and legacy currencies.
- The Bank for International Settlements (BIS) wants to contain 'crypto' risks. A report titled "Cryptocurrencies and Decentralised Finance: Functions and Financial Stability Implications" calls for expanding research into "how new forms of central bank money, capital controls, and taxation policies can counter the risks of widespread crypto adoption while still fostering technological innovation."
- "Global Implications of Scam Centres, Underground Banking, and Illicit Online Marketplaces in Southeast Asia." According to the United Nations Office on Drugs and Crime (UNODC) report, criminal organizations from East and Southeast Asia are swiftly extending their global reach. These groups are moving beyond traditional scams and trafficking, creating sophisticated online networks that include unlicensed cryptocurrency exchanges, encrypted communication platforms, and stablecoins, fueling a massive fraud economy on an industrial scale.
- Slovenia is considering a 25% capital gains tax on Bitcoin profits for individuals. The Ministry of Finance has proposed legislation to impose this tax on gains from cryptocurrency transactions, though exchanging one cryptocurrency for another would remain exempt. At present, individual 'crypto' traders in Slovenia are not taxed.
- Circle, BitGo, Coinbase, and Paxos plan to apply for U.S. bank charters or licenses. According to a report in The Wall Street Journal, major crypto companies are planning to apply for U.S. bank charters or licenses. These firms are pursuing limited licenses that would permit them to issue stablecoins, as the U.S. Congress deliberates on legislation mandating licensing for stablecoin issuers.
"Established banks, like Bank of America, are hoping to amend the current drafts of [stablecoin] legislation in such a way that nonbanks are more heavily restricted from issuing stablecoins," people familiar with the matter told The Block.
- Charles Schwab to launch spot Bitcoin trading by 2026. The financial investment firm, managing over $10 trillion in assets, has revealed plans to introduce spot Bitcoin trading for its clients within the next year.
Use the tools
- Bitcoin Safe v1.2.3 expands QR SignMessage compatibility for all QR-UR-compatible hardware signers (SpecterDIY, KeyStone, Passport, Jade; already supported COLDCARD Q). It also adds the ability to import wallets via QR, ensuring compatibility with Keystone's latest firmware (2.0.6), alongside other improvements.
- Minibits v0.2.2-beta, an ecash wallet for Android devices, packages many changes to align the project with the planned iOS app release. New features and improvements include the ability to lock ecash to a receiver's pubkey, faster confirmations of ecash minting and payments thanks to WebSockets, UI-related fixes, and more.
- Zeus v0.11.0-alpha1 introduces Cashu wallets tied to embedded LND wallets. Navigate to Settings > Ecash to enable it. Other wallet types can still sweep funds from Cashu tokens. Zeus Pay now supports Cashu address types in Zaplocker, Cashu, and NWC modes.
- LNDg v1.10.0, an advanced web interface designed for analyzing Lightning Network Daemon (LND) data and automating node management tasks, introduces performance improvements, adds a new metrics page for unprofitable and stuck channels, and displays warnings for batch openings. The Profit and Loss Chart has been updated to include on-chain costs. Advanced settings have been added for users who would like their channel database size to be read remotely (the default remains local). Additionally, the AutoFees tool now uses aggregated pubkey metrics for multiple channels with the same peer.
- Nunchuk Desktop v1.9.45 release brings the latest bug fixes and improvements.
- Blockstream Green iOS v4.1.8 has renamed L-BTC to LBTC, and improves translations of notifications, login time, and background payments.
- Blockstream Green Android v4.1.8 has added language preference in App Settings and enables an Android data backup option for disaster recovery. Additionally, it fixes issues with Jade entry point PIN timeout and Trezor passphrase input.
- Torq v2.2.2, an advanced Lightning node management software designed to handle large nodes with over 1000 channels, fixes bugs that caused channel balance to not be updated in some cases and channel "peer total local balance" not getting updated.
- Stack Wallet v2.1.12, a multicoin wallet by Cypher Stack, fixes an issue with Xelis introduced in the latest release for Windows.
- ESP-Miner-NerdQAxePlus v1.0.29.1, a forked version from the NerdAxe miner that was modified for use on the NerdQAxe+, is now available.
- Zark enables sending sats to an npub using Bark.
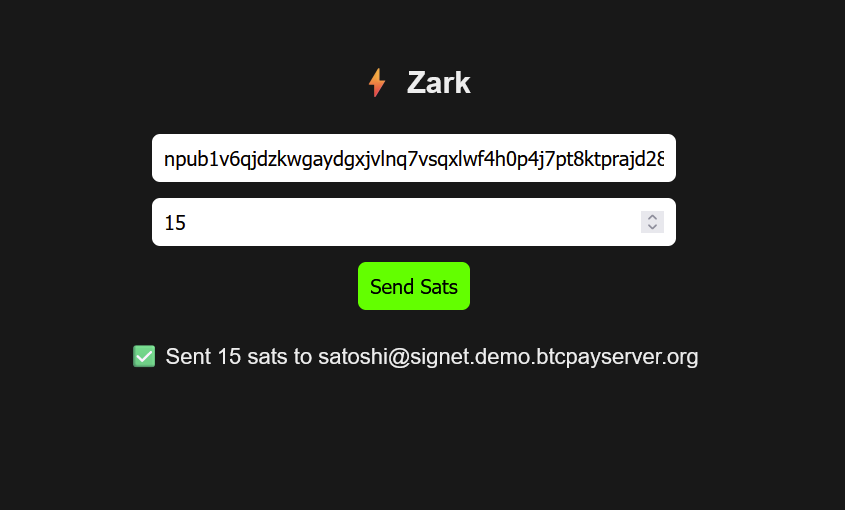
- Erk is a novel variation of the Ark protocol that completely removes the need for user interactivity in rounds, addressing one of Ark's key limitations: the requirement for users to come online before their VTXOs expire.
- Aegis v0.1.1 is now available. It is a Nostr event signer app for iOS devices.
- Nostash is a NIP-07 Nostr signing extension for Safari. It is a fork of Nostore and is maintained by Terry Yiu. Available on iOS TestFlight.
- Amber v3.2.8, a Nostr event signer for Android, delivers the latest fixes and improvements.
- Nostur v1.20.0, a Nostr client for iOS, adds
-
 @ 6d5c826a:4b27b659
2025-05-23 21:52:06
@ 6d5c826a:4b27b659
2025-05-23 21:52:06- Docker Compose - Define and run multi-container Docker applications. (Source Code)
Apache-2.0Go - Docker Swarm - Manage cluster of Docker Engines. (Source Code)
Apache-2.0Go - Docker - Platform for developers and sysadmins to build, ship, and run distributed applications. (Source Code)
Apache-2.0Go - LXC - Userspace interface for the Linux kernel containment features. (Source Code)
GPL-2.0C - LXD - Container "hypervisor" and a better UX for LXC. (Source Code)
Apache-2.0Go - OpenVZ - Container-based virtualization for Linux. (Source Code)
GPL-2.0C - Podman - Daemonless container engine for developing, managing, and running OCI Containers on your Linux System. Containers can either be run as root or in rootless mode. Simply put:
alias docker=podman. (Source Code)Apache-2.0Go - Portainer Community Edition - Simple management UI for Docker. (Source Code)
ZlibGo - systemd-nspawn - Lightweight, chroot-like, environment to run an OS or command directly under systemd. (Source Code)
GPL-2.0C
- Docker Compose - Define and run multi-container Docker applications. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:49:50
@ 6d5c826a:4b27b659
2025-05-23 21:49:50- Consul - Consul is a tool for service discovery, monitoring and configuration. (Source Code)
MPL-2.0Go - etcd - Distributed K/V-Store, authenticating via SSL PKI and a REST HTTP Api for shared configuration and service discovery. (Source Code)
Apache-2.0Go - ZooKeeper - ZooKeeper is a centralized service for maintaining configuration information, naming, providing distributed synchronization, and providing group services. (Source Code)
Apache-2.0Java/C++
- Consul - Consul is a tool for service discovery, monitoring and configuration. (Source Code)
-
 @ dfa02707:41ca50e3
2025-05-24 05:00:54
@ dfa02707:41ca50e3
2025-05-24 05:00:54News
- Wallet of Satoshi teases a comeback in the US market with a non-custodial product. According to an announcement on X, the widely popular custodial Lightning wallet is preparing to re-enter the United States market with a non-custodial wallet. It is unclear whether the product will be open-source, but the project has clarified that "there will be no KYC on any Wallet of Satoshi, ever!" Wallet of Satoshi ceased serving customers in the United States in November 2023.
- Vulnerability disclosure: Remote crash due to addr message spam in Bitcoin Core versions before v29. Bitcoin Core developer Antoine Poinsot disclosed an integer overflow bug that crashes a node if spammed with addr messages over an extended period. A fix was released on April 14, 2025, in Bitcoin Core v29.0. The issue is rated Low severity.
- Coinbase Know Your Customer (KYC) data leak. The U.S. Department of Justice, including its Criminal Division in Washington, is investigating a cyberattack on Coinbase. The incident involved cybercriminals attempting to extort $20 million from Coinbase to prevent stolen customer data from being leaked online. Although the data breach affected less than 1% of the exchange's users, Coinbase now faces at least six lawsuits following the revelation that some customer support agents were bribed as part of the extortion scheme.
- Fold has launched Bitcoin Gift Cards, enabling users to purchase bitcoin for personal use or as gifts, redeemable via the Fold app. These cards are currently available on Fold’s website and are planned to expand to major retailers nationwide later this year.
"Our mission is to make bitcoin simple and approachable for everyone. The Bitcoin Gift Card brings bitcoin to millions of Americans in a familiar way. Available at the places people already shop, the Bitcoin Gift Card is the best way to gift bitcoin to others," said Will Reeves, Chairman and CEO of Fold.
- Corporate treasuries hold nearly 1.1 million BTC, representing about 5.5% of the total circulating supply (1,082,164 BTC), per BitcoinTreasuries.net data. Recent purchases include Strategy adding 7,390 BTC (total: 576,230 BTC), Metplanet acquiring 1,004 BTC (total: 7,800 BTC), Tether holding over 100,521 BTC, and XXI Capital, led by Jack Mallers, starting with 31,500 BTC.
- Meanwhile, a group of investors has filed a class action lawsuit against Strategy and its executive Michael Saylor. The lawsuit alleges that Strategy made overly optimistic projections using fair value accounting under new FASB rules while downplaying potential losses.
- The U.S. Senate voted to advance the GENIUS stablecoin bill for further debate before a final vote to pass it. Meanwhile, the House is crafting its own stablecoin legislation to establish a regulatory framework for stablecoins and their issuers in the U.S, reports CoinDesk.
- French 'crypto' entrepreneurs get priority access to emergency police services. French Minister of the Interior, Bruno Retailleau, agreed on measures to enhance security for 'crypto' professionals during a meeting on Friday. This follows a failed kidnapping attempt on Tuesday targeting the family of a cryptocurrency exchange CEO, and two other kidnappings earlier this year.
- Brussels Court declares tracking-based ads illegal in EU. The Brussels Court of Appeal ruled tracking-based online ads illegal in the EU due to an inadequate consent model. Major tech firms like Microsoft, Amazon, Google, and X are affected by the decision, as their consent pop-ups fail to protect privacy in real-time bidding, writes The Record.
- Telegram shares data on 22,777 users in Q1 2025, a significant increase from the 5,826 users' data shared during the same period in 2024. This significant increase follows the arrest of CEO and founder Pavel Durov last year.
- An Australian judge has ruled that Bitcoin is money, potentially exempting it from capital gains tax in the country. If upheld on appeal, this interim decision could lead to taxpayer refunds worth up to $1 billion, per tax lawyer Adrian Cartland.
Use the tools
- Bitcoin Safe v1.3.0 a secure and user-friendly Bitcoin savings wallet for beginners and advanced users, introduces an interactive chart, Child Pays For Parent (CPFP) support, testnet4 compatibility, preconfigured testnet demo wallets, various bug fixes, and other improvements.
- BlueWallet v7.1.8 brings numerous bug fixes, dependency updates, and a new search feature for addresses and transactions.
- Aqua Wallet v0.3.0 is out, offering beta testing for the reloadable Dolphin card (in partnership with Visa) for spending bitcoin and Liquid BTC. It also includes a new Optical Character Recognition (OCR) text scanner to read text addresses like QR codes, colored numbers on addresses for better readability, a reduced minimum for spending and swapping Liquid Bitcoin to 100 sats, plus other fixes and enhancements.

Source: Aqua wallet.
- The latest firmware updates for COLDCARD Mk4 v5.4.3 and Q v1.3.3 are now available, featuring the latest enhancements and bug fixes.
- Nunchuk Android v1.9.68.1 and iOS v1.9.79 introduce support for custom blockchain explorers, wallet archiving, re-ordering wallets on the home screen via long-press, and an anti-fee sniping setting.
- BDK-cli v1.0.0, a CLI wallet library and REPL tool to demo and test the BDK library, now uses bdk_wallet 1.0.0 and integrates Kyoto, utilizing the Kyoto protocol for compact block filters. It sets SQLite as the default database and discontinues support for sled.
- publsp is a new command-line tool designed for Lightning node runners or Lightning Service Providers (LSPs) to advertise liquidity offers over Nostr.
"LSPs advertise liquidity as addressable Kind 39735 events. Clients just pull and evaluate all those structured events, then NIP-17 DM an LSP of their choice to coordinate a liquidity purchase," writes developer smallworlnd.
-
Lightning Blinder by Super Testnet is a proof-of-concept privacy tool for the Lightning Network. It enables users to mislead Lightning Service Providers (LSPs) by making it appear as though one wallet is the sender or recipient, masking the original wallet. Explore and try it out here.
-
Mempal v1.5.3, a Bitcoin mempool monitoring and notification app for Android, now includes a swipe-down feature to refresh the dashboard, a custom time option for widget auto-update frequency, and a
-
 @ 6d5c826a:4b27b659
2025-05-23 21:49:30
@ 6d5c826a:4b27b659
2025-05-23 21:49:30- DD-WRT - A Linux-based firmware for wireless routers and access points, originally designed for the Linksys WRT54G series. (Source Code)
GPL-2.0C - OpenWrt - A Linux-based router featuring Mesh networking, IPS via snort and AQM among many other features. (Source Code)
GPL-2.0C - OPNsense - An open source FreeBSD-based firewall and router with traffic shaping, load balancing, and virtual private network capabilities. (Source Code)
BSD-2-ClauseC/PHP - pfSense CE - Free network firewall distribution, based on the FreeBSD operating system with a custom kernel and including third party free software packages for additional functionality. (Source Code)
Apache-2.0Shell/PHP/Other
- DD-WRT - A Linux-based firmware for wireless routers and access points, originally designed for the Linksys WRT54G series. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:49:12
@ 6d5c826a:4b27b659
2025-05-23 21:49:12- Remmina - Feature-rich remote desktop application for linux and other unixes. (Source Code)
GPL-2.0C - Tiger VNC - High-performance, multi-platform VNC client and server. (Source Code)
GPL-2.0C++ - X2go - X2Go is an open source remote desktop software for Linux that uses the NoMachine/NX technology protocol. (Source Code)
GPL-2.0Perl
- Remmina - Feature-rich remote desktop application for linux and other unixes. (Source Code)
-
 @ c1e9ab3a:9cb56b43
2025-05-18 04:14:48
@ c1e9ab3a:9cb56b43
2025-05-18 04:14:48Abstract
This document proposes a novel architecture that decouples the peer-to-peer (P2P) communication layer from the Bitcoin protocol and replaces or augments it with the Nostr protocol. The goal is to improve censorship resistance, performance, modularity, and maintainability by migrating transaction propagation and block distribution to the Nostr relay network.
Introduction
Bitcoin’s current architecture relies heavily on its P2P network to propagate transactions and blocks. While robust, it has limitations in terms of flexibility, scalability, and censorship resistance in certain environments. Nostr, a decentralized event-publishing protocol, offers a multi-star topology and a censorship-resistant infrastructure for message relay.
This proposal outlines how Bitcoin communication could be ported to Nostr while maintaining consensus and verification through standard Bitcoin clients.
Motivation
- Enhanced Censorship Resistance: Nostr’s architecture enables better relay redundancy and obfuscation of transaction origin.
- Simplified Lightweight Nodes: Removing the full P2P stack allows for lightweight nodes that only verify blockchain data and communicate over Nostr.
- Architectural Modularity: Clean separation between validation and communication enables easier auditing, upgrades, and parallel innovation.
- Faster Propagation: Nostr’s multi-star network may provide faster propagation of transactions and blocks compared to the mesh-like Bitcoin P2P network.
Architecture Overview
Components
-
Bitcoin Minimal Node (BMN):
- Verifies blockchain and block validity.
- Maintains UTXO set and handles mempool logic.
- Connects to Nostr relays instead of P2P Bitcoin peers.
-
Bridge Node:
- Bridges Bitcoin P2P traffic to and from Nostr relays.
- Posts new transactions and blocks to Nostr.
- Downloads mempool content and block headers from Nostr.
-
Nostr Relays:
- Accept Bitcoin-specific event kinds (transactions and blocks).
- Store mempool entries and block messages.
- Optionally broadcast fee estimation summaries and tipsets.
Event Format
Proposed reserved Nostr
kindnumbers for Bitcoin content (NIP/BIP TBD):| Nostr Kind | Purpose | |------------|------------------------| | 210000 | Bitcoin Transaction | | 210001 | Bitcoin Block Header | | 210002 | Bitcoin Block | | 210003 | Mempool Fee Estimates | | 210004 | Filter/UTXO summary |
Transaction Lifecycle
- Wallet creates a Bitcoin transaction.
- Wallet sends it to a set of configured Nostr relays.
- Relays accept and cache the transaction (based on fee policies).
- Mining nodes or bridge nodes fetch mempool contents from Nostr.
- Once mined, a block is submitted over Nostr.
- Nodes confirm inclusion and update their UTXO set.
Security Considerations
- Sybil Resistance: Consensus remains based on proof-of-work. The communication path (Nostr) is not involved in consensus.
- Relay Discoverability: Optionally bootstrap via DNS, Bitcoin P2P, or signed relay lists.
- Spam Protection: Relay-side policy, rate limiting, proof-of-work challenges, or Lightning payments.
- Block Authenticity: Nodes must verify all received blocks and reject invalid chains.
Compatibility and Migration
- Fully compatible with current Bitcoin consensus rules.
- Bridge nodes preserve interoperability with legacy full nodes.
- Nodes can run in hybrid mode, fetching from both P2P and Nostr.
Future Work
- Integration with watch-only wallets and SPV clients using verified headers via Nostr.
- Use of Nostr’s social graph for partial trust assumptions and relay reputation.
- Dynamic relay discovery using Nostr itself (relay list events).
Conclusion
This proposal lays out a new architecture for Bitcoin communication using Nostr to replace or augment the P2P network. This improves decentralization, censorship resistance, modularity, and speed, while preserving consensus integrity. It encourages innovation by enabling smaller, purpose-built Bitcoin nodes and offloading networking complexity.
This document may become both a Bitcoin Improvement Proposal (BIP-XXX) and a Nostr Improvement Proposal (NIP-XXX). Event kind range reserved: 210000–219999.
-
 @ 2f29aa33:38ac6f13
2025-05-17 12:59:01
@ 2f29aa33:38ac6f13
2025-05-17 12:59:01The Myth and the Magic
Picture this: a group of investors, huddled around a glowing computer screen, nervously watching Bitcoin’s price. Suddenly, someone produces a stick-no ordinary stick, but a magical one. With a mischievous grin, they poke the Bitcoin. The price leaps upward. Cheers erupt. The legend of the Bitcoin stick is born.
But why does poking Bitcoin with a stick make the price go up? Why does it only work for a lucky few? And what does the data say about this mysterious phenomenon? Let’s dig in, laugh a little, and maybe learn the secret to market-moving magic.

The Statistical Side of Stick-Poking
Bitcoin’s Price: The Wild Ride
Bitcoin’s price is famous for its unpredictability. In the past year, it’s soared, dipped, and soared again, sometimes gaining more than 50% in just a few months. On a good day, billions of dollars flow through Bitcoin trades, and the price can jump thousands in a matter of hours. Clearly, something is making this happen-and it’s not just spreadsheets and financial news.
What Actually Moves the Price?
-
Scarcity: Only 21 million Bitcoins will ever exist. When more people want in, the price jumps.
-
Big News: Announcements, rumors, and meme-worthy moments can send the price flying.
-
FOMO: When people see Bitcoin rising, they rush to buy, pushing it even higher.
-
Liquidations: When traders betting against Bitcoin get squeezed, it triggers a chain reaction of buying.
But let’s be honest: none of this is as fun as poking Bitcoin with a stick.

The Magical Stick: Not Your Average Twig
Why Not Every Stick Works
You can’t just grab any old branch and expect Bitcoin to dance. The magical stick is a rare artifact, forged in the fires of internet memes and blessed by the spirit of Satoshi. Only a chosen few possess it-and when they poke, the market listens.
Signs You Have the Magical Stick
-
When you poke, Bitcoin’s price immediately jumps a few percent.
-
Your stick glows with meme energy and possibly sparkles with digital dust.
-
You have a knack for timing your poke right after a big event, like a halving or a celebrity tweet.
-
Your stick is rumored to have been whittled from the original blockchain itself.
Why Most Sticks Fail
-
No Meme Power: If your stick isn’t funny, Bitcoin ignores you.
-
Bad Timing: Poking during a bear market just annoys the blockchain.
-
Not Enough Hype: If the bitcoin community isn’t watching, your poke is just a poke.
-
Lack of Magic: Some sticks are just sticks. Sad, but true.

The Data: When the Stick Strikes
Let’s look at some numbers:
-
In the last month, Bitcoin’s price jumped over 20% right after a flurry of memes and stick-poking jokes.
-
Over the past year, every major price surge was accompanied by a wave of internet hype, stick memes, or wild speculation.
-
In the past five years, Bitcoin’s biggest leaps always seemed to follow some kind of magical event-whether a halving, a viral tweet, or a mysterious poke.
Coincidence? Maybe. But the pattern is clear: the stick works-at least when it’s magical.

The Role of Memes, Magic, and Mayhem
Bitcoin’s price is like a cat: unpredictable, easily startled, and sometimes it just wants to be left alone. But when the right meme pops up, or the right stick pokes at just the right time, the price can leap in ways that defy logic.
The bitcoin community knows this. That’s why, when Bitcoin’s stuck in a rut, you’ll see a flood of stick memes, GIFs, and magical thinking. Sometimes, it actually works.

The Secret’s in the Stick (and the Laughs)
So, does poking Bitcoin with a stick really make the price go up? If your stick is magical-blessed by memes, timed perfectly, and watched by millions-absolutely. The statistics show that hype, humor, and a little bit of luck can move markets as much as any financial report.
Next time you see Bitcoin stalling, don’t just sit there. Grab your stick, channel your inner meme wizard, and give it a poke. Who knows? You might just be the next legend in the world of bitcoin magic.
And if your stick doesn’t work, don’t worry. Sometimes, the real magic is in the laughter along the way.

-aco
@block height: 897,104
-
-
 @ 6d5c826a:4b27b659
2025-05-23 21:48:56
@ 6d5c826a:4b27b659
2025-05-23 21:48:56- ActiveMQ - Java message broker. (Source Code)
Apache-2.0Java - BeanstalkD - A simple, fast work queue. (Source Code)
MITC - Gearman - Fast multi-language queuing/job processing platform. (Source Code)
BSD-3-ClauseC++ - NSQ - A realtime distributed messaging platform. (Source Code)
MPL-2.0Go - ZeroMQ - Lightweight queuing system. (Source Code)
GPL-3.0C++
- ActiveMQ - Java message broker. (Source Code)
-
 @ 3c389c8f:7a2eff7f
2025-05-23 21:35:30
@ 3c389c8f:7a2eff7f
2025-05-23 21:35:30Web:
https://shopstr.store/
https://cypher.space/
https://plebeian.market/
Mobile:
https://www.amethyst.social/
-
 @ 6d5c826a:4b27b659
2025-05-23 21:48:36
@ 6d5c826a:4b27b659
2025-05-23 21:48:36- aptly - Swiss army knife for Debian repository management. (Source Code)
MITGo - fpm - Versatile multi format package creator. (Source Code)
MITRuby - omnibus-ruby - Easily create full-stack installers for your project across a variety of platforms.
Apache-2.0Ruby - tito - Builds RPMs for git-based projects.
GPL-2.0Python
- aptly - Swiss army knife for Debian repository management. (Source Code)
-
 @ 3c389c8f:7a2eff7f
2025-05-23 21:27:26
@ 3c389c8f:7a2eff7f
2025-05-23 21:27:26Clients:
https://untype.app
https://habla.news
https://yakihonne.com
https://cypher.space
https://highlighter.com
https://pareto.space/en
https://comet.md/
Plug Ins:
https://github.com/jamesmagoo/nostr-writer
https://threenine.co.uk/products/obstrlish
Content Tagging:
https://labelmachine.org
https://ontolo.social
Blog-like Display and Personal Pages:
https://orocolo.me
https://npub.pro
Personal Notes and Messaging:
https://app.flotilla.social There's an app, too!
https://nosbin.com
RSS Readers:
https://nostrapps.com/noflux
https://nostrapps.com/narr
https://nostrapps.com/feeder
-
 @ 6d5c826a:4b27b659
2025-05-23 21:48:21
@ 6d5c826a:4b27b659
2025-05-23 21:48:21- CapRover - Build your own PaaS in a few minutes. (Demo, Source Code)
Apache-2.0Docker/Nodejs - Coolify - An open-source & self-hostable Heroku / Netlify alternative (and even more). (Source Code)
Apache-2.0Docker - Dokku - An open-source PaaS (alternative to Heroku). (Source Code)
MITDocker/Shell/Go/deb - fx - A tool to help you do Function as a Service with painless on your own servers.
MITGo - Kubero - A self-hosted Heroku PaaS alternative for Kubernetes that implements GitOps. (Demo, Source Code)
GPL-3.0K8S/Nodejs/Go - LocalStack - LocalStack is a fully functional local AWS cloud stack. This includes Lambda for serverless computation. (Source Code)
Apache-2.0Python/Docker/K8S - Nhost - Firebase Alternative with GraphQL. Get a database and backend configured and ready in minutes. (Source Code)
MITDocker/Nodejs/Go - OpenFaaS - Serverless Functions Made Simple for Docker & Kubernetes. (Source Code)
MITGo - Tau - Easily build Cloud Computing Platforms with features like Serverless WebAssembly Functions, Frontend Hosting, CI/CD, Object Storage, K/V Database, and Pub-Sub Messaging. (Source Code)
BSD-3-ClauseGo/Rust/Docker - Trusted-CGI - Lightweight self-hosted lambda/applications/cgi/serverless-functions platform.
MITGo/deb/Docker
- CapRover - Build your own PaaS in a few minutes. (Demo, Source Code)
-
 @ c1e9ab3a:9cb56b43
2025-05-09 23:10:14
@ c1e9ab3a:9cb56b43
2025-05-09 23:10:14I. Historical Foundations of U.S. Monetary Architecture
The early monetary system of the United States was built atop inherited commodity money conventions from Europe’s maritime economies. Silver and gold coins—primarily Spanish pieces of eight, Dutch guilders, and other foreign specie—formed the basis of colonial commerce. These units were already integrated into international trade and piracy networks and functioned with natural compatibility across England, France, Spain, and Denmark. Lacking a centralized mint or formal currency, the U.S. adopted these forms de facto.
As security risks and the practical constraints of physical coinage mounted, banks emerged to warehouse specie and issue redeemable certificates. These certificates evolved into fiduciary media—claims on specie not actually in hand. Banks observed over time that substantial portions of reserves remained unclaimed for years. This enabled fractional reserve banking: issuing more claims than reserves held, so long as redemption demand stayed low. The practice was inherently unstable, prone to panics and bank runs, prompting eventual centralization through the formation of the Federal Reserve in 1913.
Following the Civil War and unstable reinstatements of gold convertibility, the U.S. sought global monetary stability. After World War II, the Bretton Woods system formalized the U.S. dollar as the global reserve currency. The dollar was nominally backed by gold, but most international dollars were held offshore and recycled into U.S. Treasuries. The Nixon Shock of 1971 eliminated the gold peg, converting the dollar into pure fiat. Yet offshore dollar demand remained, sustained by oil trade mandates and the unique role of Treasuries as global reserve assets.
II. The Structure of Fiduciary Media and Treasury Demand
Under this system, foreign trade surpluses with the U.S. generate excess dollars. These surplus dollars are parked in U.S. Treasuries, thereby recycling trade imbalances into U.S. fiscal liquidity. While technically loans to the U.S. government, these purchases act like interest-only transfers—governments receive yield, and the U.S. receives spendable liquidity without principal repayment due in the short term. Debt is perpetually rolled over, rarely extinguished.
This creates an illusion of global subsidy: U.S. deficits are financed via foreign capital inflows that, in practice, function more like financial tribute systems than conventional debt markets. The underlying asset—U.S. Treasury debt—functions as the base reserve asset of the dollar system, replacing gold in post-Bretton Woods monetary logic.
III. Emergence of Tether and the Parastatal Dollar
Tether (USDT), as a private issuer of dollar-denominated tokens, mimics key central bank behaviors while operating outside the regulatory perimeter. It mints tokens allegedly backed 1:1 by U.S. dollars or dollar-denominated securities (mostly Treasuries). These tokens circulate globally, often in jurisdictions with limited banking access, and increasingly serve as synthetic dollar substitutes.
If USDT gains dominance as the preferred medium of exchange—due to technological advantages, speed, programmability, or access—it displaces Federal Reserve Notes (FRNs) not through devaluation, but through functional obsolescence. Gresham’s Law inverts: good money (more liquid, programmable, globally transferable USDT) displaces bad (FRNs) even if both maintain a nominal 1:1 parity.
Over time, this preference translates to a systemic demand shift. Actors increasingly use Tether instead of FRNs, especially in global commerce, digital marketplaces, or decentralized finance. Tether tokens effectively become shadow base money.
IV. Interaction with Commercial Banking and Redemption Mechanics
Under traditional fractional reserve systems, commercial banks issue loans denominated in U.S. dollars, expanding the money supply. When borrowers repay loans, this destroys the created dollars and contracts monetary elasticity. If borrowers repay in USDT instead of FRNs:
- Banks receive a non-Fed liability (USDT).
- USDT is not recognized as reserve-eligible within the Federal Reserve System.
- Banks must either redeem USDT for FRNs, or demand par-value conversion from Tether to settle reserve requirements and balance their books.
This places redemption pressure on Tether and threatens its 1:1 peg under stress. If redemption latency, friction, or cost arises, USDT’s equivalence to FRNs is compromised. Conversely, if banks are permitted or compelled to hold USDT as reserve or regulatory capital, Tether becomes a de facto reserve issuer.
In this scenario, banks may begin demanding loans in USDT, mirroring borrower behavior. For this to occur sustainably, banks must secure Tether liquidity. This creates two options: - Purchase USDT from Tether or on the secondary market, collateralized by existing fiat. - Borrow USDT directly from Tether, using bank-issued debt as collateral.
The latter mirrors Federal Reserve discount window operations. Tether becomes a lender of first resort, providing monetary elasticity to the banking system by creating new tokens against promissory assets—exactly how central banks function.
V. Structural Consequences: Parallel Central Banking
If Tether begins lending to commercial banks, issuing tokens backed by bank notes or collateralized debt obligations: - Tether controls the expansion of broad money through credit issuance. - Its balance sheet mimics a central bank, with Treasuries and bank debt as assets and tokens as liabilities. - It intermediates between sovereign debt and global liquidity demand, replacing the Federal Reserve’s open market operations with its own issuance-redemption cycles.
Simultaneously, if Tether purchases U.S. Treasuries with FRNs received through token issuance, it: - Supplies the Treasury with new liquidity (via bond purchases). - Collects yield on government debt. - Issues a parallel form of U.S. dollars that never require redemption—an interest-only loan to the U.S. government from a non-sovereign entity.
In this context, Tether performs monetary functions of both a central bank and a sovereign wealth fund, without political accountability or regulatory transparency.
VI. Endgame: Institutional Inversion and Fed Redundancy
This paradigm represents an institutional inversion:
- The Federal Reserve becomes a legacy issuer.
- Tether becomes the operational base money provider in both retail and interbank contexts.
- Treasuries remain the foundational reserve asset, but access to them is mediated by a private intermediary.
- The dollar persists, but its issuer changes. The State becomes a fiscal agent of a decentralized financial ecosystem, not its monetary sovereign.
Unless the Federal Reserve reasserts control—either by absorbing Tether, outlawing its instruments, or integrating its tokens into the reserve framework—it risks becoming irrelevant in the daily function of money.
Tether, in this configuration, is no longer a derivative of the dollar—it is the dollar, just one level removed from sovereign control. The future of monetary sovereignty under such a regime is post-national and platform-mediated.
-
 @ bf47c19e:c3d2573b
2025-05-23 21:17:02
@ bf47c19e:c3d2573b
2025-05-23 21:17:02Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Šta uzrokuje Inflaciju?
- Da li nam je infacija potrebna?
- Kako se meri inflacija?
- Da li inflacija pokreće ekonomski rast?
- Da li inflacija pokreće ili umanjuje nejednakost bogatstva?
- Gde se danas javlja inflacija?
- Šta je deflacija?
- Kakav uticaj inflacija ima na društvo?
Inflacija može da bude uznemirujuća tema, jer uključuje amorfni koncept novca. Međutim, inflacija je zapravo jednostavna tema koja je napravljena da bude složena razdvajanjem novca i drugih dobara. U ovom članku razlažemo inflaciju i njene uzroke.
Najjednostavnija definicija inflacije je rast cena dobara i usluga. Kada cene rastu, to takođe znači da vrednost jedinice novca – poput dolara – opada. Uzmimo primer McDonald’s hamburgera: 1955. ovaj skromni hamburger se prodavao za samo 15 centi. U 2018. godini se prodavao za 1,09 USD. U 2021. godini prodaje se za 2,49 USD – ogroman rast cene od 1650%.
To znači da je dolar izgubio dosta svoje vrednosti. 1955. godine mogli ste da kupite gotovo 7 hamburgera za novčanicu od jednog dolara. 2021. godine taj dolar vam ne bi kupio ni jedan hamburger. Zašto se čini da cene uvek rastu tokom vremena? I šta možete da učinite povodom toga? Ovaj članak ima za cilj da odgovori na ta pitanja.
Ekonomisti pokušavaju da sumiraju rast cena mnogih dobara i usluga kao jedan prosečan broj. Ovaj broj predstavlja promenu ukupnih troškova u godišnjim troškovima prosečnog potrošača, kao što su stanarina, hrana i gorivo.
U Sjedinjenim Državama ovaj broj je poznat kao Indeks Potrošačkih Cena, eng. Consumer Price Index (CPI). Kada se CPI poveća tokom određenog vremenskog perioda, ekonomisti kažu da imamo inflaciju. Kada se smanji, to se naziva deflacija.
Šta uzrokuje Inflaciju?
Mnogi izvori kažu da je stalna inflacija koju danas doživljavamo ili uzrokovana povećanjem potražnje (eng. demand-pull) ili smanjenjem ponude usled povećanih proizvodnih troškova (eng. cost-push).
Ovi razlozi nisu tačni – hajde da pogledamo zašto.
Da bismo razumeli pravi razlog inflacije, moramo da sagledamo dve vrste inflacije:
- Inflacija Cena: Cene vremenom rastu.
- Monetarna Inflacija: Količina valute u opticaju raste sa vremenom.
Prva, inflacija cena, retko se javlja tokom dužih perioda (decenije, vekovi) zbog povećane potražnje ili povećanih troškova. Zašto? Tržišta teže da se uravnoteže. Tokom istorije smo više puta videli da povećana potražnja za dobrom povećava njegovu cenu, što podstiče proizvođače da proizvode više tog dobra. Kada se ponuda poveća, cene se smanjuju.
Ovaj ciklus može da potraje nekoliko godina, i javlja se kod gotovo svake robe i „konačnog dobra“ (automobili, televizori, hrana itd.) na Zemlji. Izuzetak su retki metali poput zlata i srebra. Dokazi o tome su prikazani u nastavku.
Kada se poveća trošak za proizvodnju dobra, cena tog dobra često raste da bi pokrila te troškove. Ovaj rast cene dovodi do toga da potrošači tog dobra traže alternativu ili smanjuju potrošnju tog dobra, što dovodi do pada cena na prethodni nivo.
Tržište se prirodno uravnotežava, a cene se smanjuju ili povećanjem ponude ili smanjenjem potražnje.
Da li imamo dokaze da tržišta vremenom uravnotežuju ponudu i potražnju?
Podaci o cenama robe tokom vremena mogu nam dati bolje razumevanje da li tržišta zaista efikasno uravnotežuju ponudu i potražnju. Međutim, cene ne možemo da posmatramo u smislu nacionalnih valuta, jer naše vlade uvek štampaju više svojih nacionalnih valuta.
Oni sprovode monetarnu inflaciju, koja može da izazove inflaciju cena. Posmatranje tržišnih cena u smislu nacionalnih valuta, poput američkog dolara, je poput merenja visine lenjirom koji se neprestano smanjuje. Vaša visina u broju biće sve veća i veća, ali stvarna visina se ne menja.
Mi možemo da znamo da li tržišta uravnotežuju ponudu i potražnju gledajući cene dobara u smislu monetarnog dobra koje ima vrlo konzistentnu ponudu tokom vremena.
Vremenom se pokazalo da zlato ima najmanju monetarnu inflaciju od svih postojećih valuta i dobara. To čini zlato odličnim ‘lenjirom’ za merenje da li tržišta vremenom uravnotežuju ponudu i potražnju. Da bismo bolje razumeli inflaciju cena tokom vremena, pitaćemo koliko unci zlata nešto košta tokom vremena.
Cene u zlatu pokazuju nam da se tržišta vremenom uravnotežuju
Ako cene dobara posmatramo u obliku zlata, vidimo da cene robe prate srednje tačke tokom dužih vremenskih perioda.
Nafta, na primer, je vrlo nestabilna, ali ima tendenciju da se kreće oko 2,5 grama zlata po barelu.
 WTI Sirova Nafta u gramima Zlata po Barelu
WTI Sirova Nafta u gramima Zlata po BareluCena nafte je promenljiva, ali tokom decenija ima tendenciju da se kreće po strani.
Cene kuća tokom proteklih 10 godina takođe su prilično stabilne, iako imamo fiksnu količinu zemlje na planeti. Vidimo da cene kuća u pogledu zlata imaju tendenciju da variraju oko indeksne cene od oko 80, prikazane na grafikonu.
 Shiller-ov US indeks cena kuća u USD i zlatu
Shiller-ov US indeks cena kuća u USD i zlatuOvaj grafikon je na logaritamskoj skali, što nam omogućava da vizualizujemo zapanjujuća povećanja u zelenoj liniji, koja predstavlja domove u dolarima.
Grafički izražene u američkim dolarima, cene ovih dobara uvek rastu – baš kao i McDonald’s hamburger. Da su povećana potražnja ili povećani troškovi odgovorni za konstantnu inflaciju cena, takođe bismo videli kako se cena ove robe povećava u smislu zlata. Podaci iznad pokazuju da su cene konstantne.
Moraju da postoje i drugi razlozi za upornu inflaciju cena koju smo videli u dolarskim iznosima tokom proteklog veka.
Evo šta znamo o tome šta dugoročno utiče na cene, kao u periodu od 1955. do 2018. godine:
- Rast produktivnosti uzrokovan inovacijama, što dovodi do pada cena tokom vremena
- Monetarna inflacija – štampanje velikih količina valute – koja uzrokuje porast cena denominovanih u toj valuti tokom vremena
Znamo da cene izražene u dolarima, eurima i ostalim valutama neprestano rastu. Ako ne mislimo da naša produktivnost kao društva ide unazad, postoji samo jedan jednostavan razlog za inflaciju cena: štampanje većih količina valute, iliti monetarna inflacija.
Naše vlade i banke su zapravo prilično iskrene u pogledu zapanjujućih količina valute koje štampaju. Oni nam svakodnevno govore da oni uzrokuju monetarnu inflaciju.
Da li nam je infacija potrebna?
Bez uporne monetarne inflacije (koja uzrokuje inflaciju cena), naša celokupna savremena ekonomija bi se srušila.

Dozvolite da vam objasnim. Sledeći odeljak može da bude šokantan, i ohrabrujem vas da i sami istražite ukoliko mislite da nisam u pravu.
Kada centralne banke i komercijalne banke daju zajmove, one stvaraju novu valutu.
Kada centralne banke daju zajmove vladama “kupujući državni dug”, one stvaraju novu valutu kada to urade. To omogućava vladama da vode budžetski deficit trošeći više nego što uzimaju od poreza. U tom procesu državni dug se nagomilava.
Komercijalne banke stvaraju novu valutu kada daju zajmove fizičkim licima i preduzećima. Jedino ograničenje koliko novog novca mogu da stvore je zakonski zahtev da banka ima na raspolaganju određeni procenat od ukupnog iznosa novca koji su ljudi deponovali. Zbog toga je naš bankarski sistem poznat kao delimična rezerva – banke pri ruci moraju da imaju samo deo vašeg novca.

Stvaranje valute je neophodno da bi održalo sistem u životu
Budući da se svi zajmovi uglavnom sastoje od novostvorene valute, mora se stvoriti još više valute da bi se taj dug otplatio. A evo i zašto:
Recimo da su prošle godine sve svetske kreditne aktivnosti dovele do stvaranja 100 milijardi dolara. Svih tih 100 milijardi dolara je novostvoreno, i one se duguju bankama sa nekom dodatnom vrednošću za kamate. Odakle dolazi ova dodatna valuta za plaćanje kamata? Budući da ovde govorimo o celokupnoj svetskoj ekonomiji, to plaćanje kamata mora da dodje iz nove količine novostvorene valute.
Sve jedinice današnjih valuta nastale su pozajmljivanjem, a isplata kamate na te zajmove znači da moramo stalno da stvaramo još više nove valute. To dovodi do beskrajne monetarne inflacije. Kada nova valuta cirkuliše kroz ekonomiju, to dovodi do porasta cena: inflacije cena.
 Previše monetarne inflacije može dovesti do hiperinflacije cena. U Venecueli je krajem 2018. godine piletina koštala preko 14 miliona Bolivara. Izvor: NBC News
Previše monetarne inflacije može dovesti do hiperinflacije cena. U Venecueli je krajem 2018. godine piletina koštala preko 14 miliona Bolivara. Izvor: NBC NewsMonetarni sistem se raspada ako se ova monetarna inflacija zaustavi, jer bi to značilo da veliki broj onih koji su uzeli zajam širom sveta ne bi mogao da vrati novac koji su pozajmili – oni ne bi izmirili svoje dugove.
Banke ili zajmodavci koji drže dug tada bi imali bezvrednu imovinu. Budući da vrednost duga podupire vrednost valute, vrednost valute bi strmoglavo padala zajedno sa dugom.
Kada ljudi izgube poverenje u ’tradicionalnu’ valutu, ona brzo postane bezvredna. To se dogodilo u Nemačkoj nakon Prvog svetskog rata, u Peruu devedesetih, Jugoslaviji 1994. ,Zimbabveu, Venecueli i sa još bezbroj drugih tradicionalnih valuta. Da bi odložile ovaj neizbežni ishod dokle god mogu, centralne banke jačaju poverenje u sistem nastavljajući da štampaju valutu stabilnim kursom.
Ovo osigurava da većina ljudi koju su uzeli zajam ima valutu za otplatu svojih kredita. Upravo to se dešava kada vlada izvrši „spas“ kao 2008. ili 2020. – oni osiguravaju da svi imaju dovoljno novca za plaćanje dugova, tako da laž može da se nastavi.
Inflacija ne dolazi iz povećanja potražnje
Sa više valute u opticaju, monetarna inflacija može da izgleda kao povećanje potražnje. Međutim, ekonomisti koji kažu da povećana potražnja pokreće stabilnu inflaciju tokom decenija propuštaju suptilnu poentu: iako monetarna inflacija može da prouzrokuje veću potrošnju, to nije zato što su ljudi zaista bogatiji, već zato što veruju da su bogatiji.
Kada se puno novca ubrizga u ekonomiju, cene jednostavno rastu jer više valute pokriva istu količinu robe. Rast cena znači pad vrednosti valute, tako da nema realnog povećanja stvarnog bogatstva, iako ljudi možda “troše više” u nominalnom iznosu valute.
Uzmimo ovaj primer: vi mesečno zarađujete 1.500 EUR, i prema svom trenutnom načinu života vi mesečno trošite oko 1.500 EUR. Dolazi vlada i počinje da vam daje dodatnih 500 EUR svakog meseca – vi se osećate poprilično dobro, zar ne? Sada možete da izlazite češće u restoran.
Međutim, vlada daje svima po 500 EUR mesečno, i svi ostali takođe troše taj novac. Ekonomista u vladinoj kancelariji, vidi da sada svi troše tih dodatnih 500 EUR mesečno i zaključuje da je vlada ‘stimulisala ekonomiju’.
Ipak, kako sav taj dodatni novac kruži ekonomijom, cene prirodno rastu. Sada vam je potrebno 2.000 EUR da biste održali svoj trenutni način života.
Da li si nešto bogatiji?
Vi možda imate više eura na vašem bankovnom računu, ali svaki od njih vam kupuje manje. Sada trošite 2.000 EUR mesečno da biste živeli životnim stilom koji vas je nekada koštao samo 1.500 EUR mesečno.
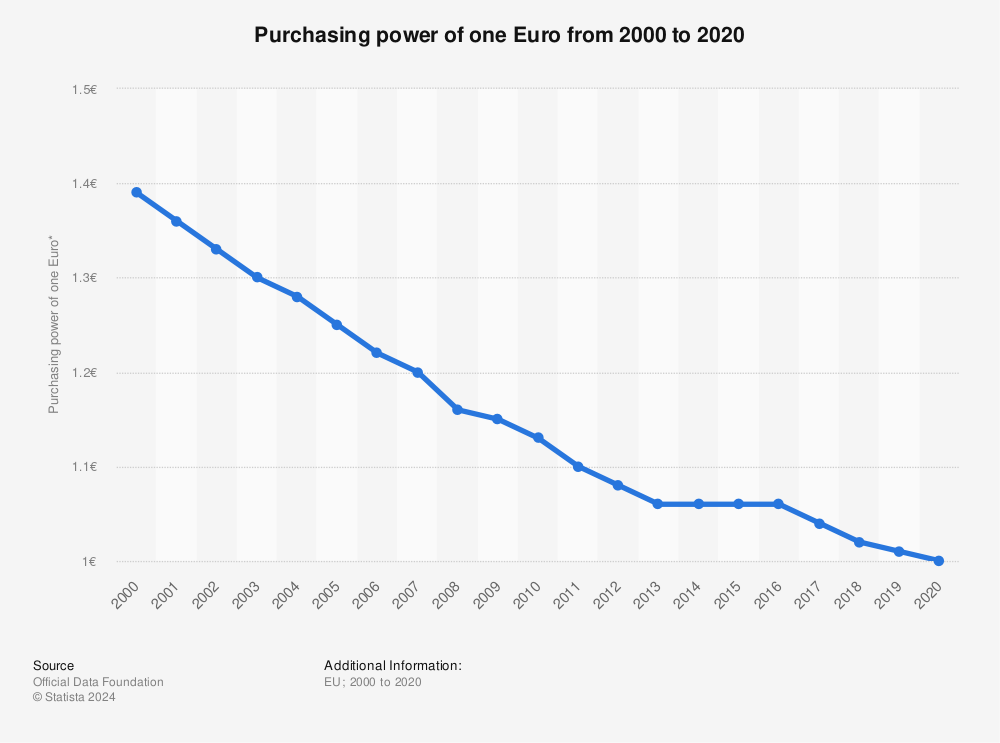
Ovo je ono što monetarna inflacija radi, i zašto je toliko pametnih ekonomista zavarano da misle da povećana potražnja, radije nego štampanje novca, pokreće trajnu inflaciju cena.
Da li smo uvek imali inflaciju?
Stalna inflacija cena relativno je nedavna pojava u modernim ekonomijama i započela je u vreme kada su Sjedinjene Države počele da konstantno štampaju valutu. Ako bi promene ponude i potražnje zaista dugoročno uzrokovale inflaciju cena, videli bismo inflaciju cena tokom istorije. Podaci govore drugačiju priču.
Indeks potrošačkih cena, koji se povećava kada imamo inflaciju cena, bio je prilično konstantan pre početka našeg trenutnog tradicionalnog ’fiat’ monetarnog sistema.
Taj sistem je započeo Bretton Woods-ovim sporazumom iz 1945. godine, a ubrzao se kada je Nixon 1971. okončao svetski zlatni standard.
 Indeks potrošačkih cena, Sjedinjene Države, 1790-2015
Indeks potrošačkih cena, Sjedinjene Države, 1790-2015Kako se meri inflacija?
Inflacija cena se često prikazuje kao promena indeksa potrošačkih cena (CPI). CPI je prosek cena raznih dobara koje ljudi kupuju u svakodnevnom životu: hrane, goriva, stanovanja itd. U Sjedinjenim Državama, vladin odsek pod nazivom Biro za statistiku rada (BLS) meri promene cena. To rade tako što posećuju maloprodajne radnje, beleže cene, računaju prosek i izveštavaju godišnju inflaciju kao promenu u odnosu na prošlu godinu.
Stopa inflacije koja se izveštava, je važna svima jer se koristi za određivanje povećanja troškova života i socijalnih davanja, poput plaćanja socijalnog osiguranja. Kada se CPI prilagodi naniže, isplate zarada i naknada su manje nego što bi trebalo da budu.
Efekti su se vremenom sjedinili: osoba koja u svojoj prvoj godini rada zaradi 40.000 USD zarađivaće samo 52.000 USD u svojoj desetoj godini staža, sa povećanim troškovima života od 3% da bi se plata podudarala sa inflacijom. Ako bi vlada umesto toga prijavila inflaciju od 6%, ta osoba bi u svojoj desetoj godini zarađivala 67.500 USD – tj. oko 30% više. Način na koji izračunavamo i prijavljujemo inflaciju ima ogroman uticaj na zaradu većine zaposlenih i građana.
Ovo je inflacija (procentualna promena u CPI) izmerena u poslednjih 20 godina u Sjedinjenim Državama:
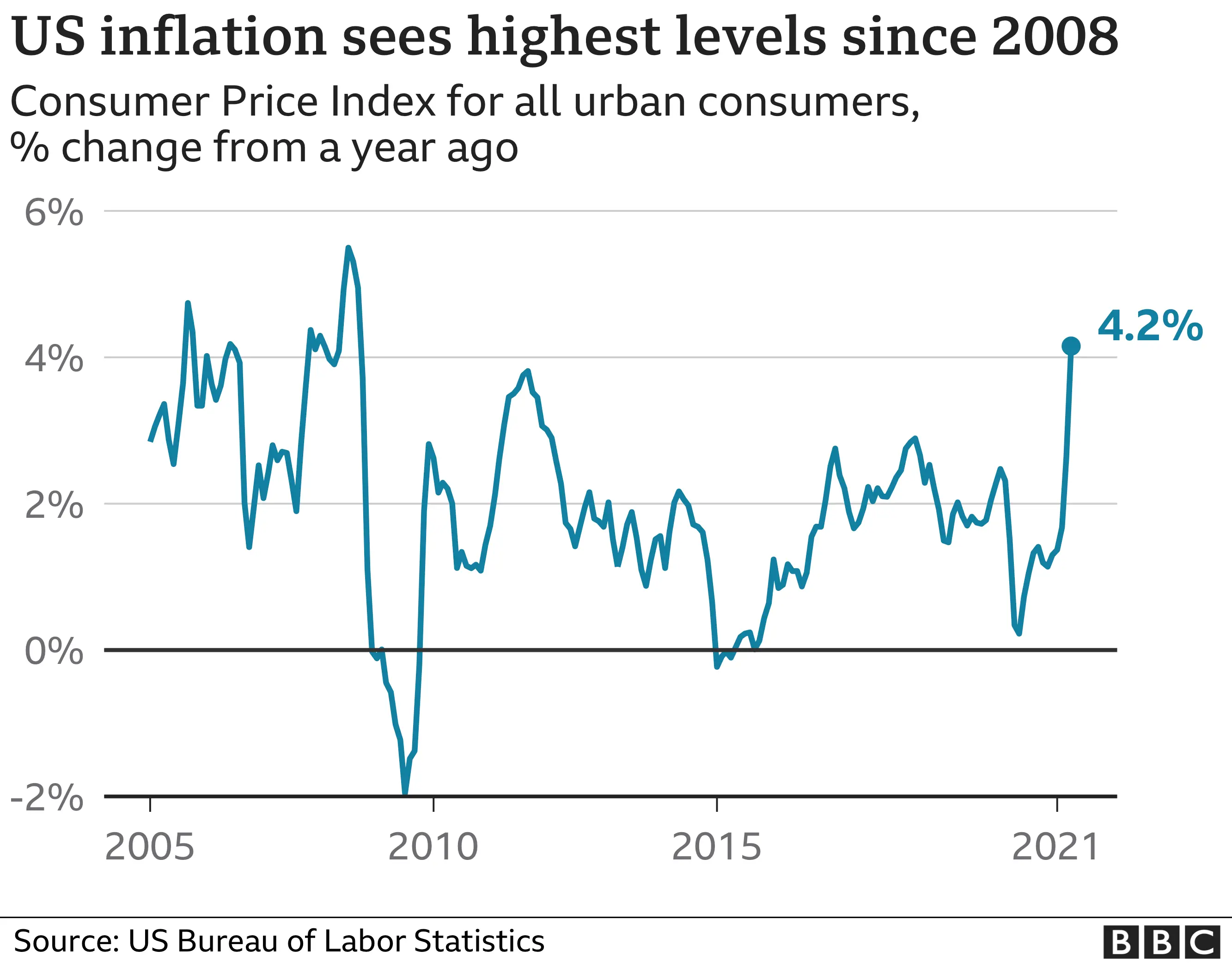
Prvobitno je BLS jednostavno beležio cenu korpe robe široke potrošnje svake godine. Međutim, istraživanje Boskinove Komisije 1996. godine dovelo je do novih alata koji Birou za statistiku rada omogućavaju prilagođavanje cena u CPI. Dva najvažnija alata su geometrijsko ponderisanje i hedonika.
Geometrijsko Ponderisanje
Geometrijsko ponderisanje znači da kupovne navike sada mogu da utiču na to koliko promena cene pojedinog dobra utiče na CPI. Ako potrošači kupe manje robe, ona ima manju težinu kada se ubaci u presek indeksa potrošačkih cena. Boskinova Komisija je tvrdila da bi ova promena pomogla da se promene sklonosti potrošača. Međutim, ne postoji način da se utvrdi da li ljudi menjaju svoje kupovne navike jer zapravo žele da kupuju različite stvari. Vrlo je moguće da ljudi kupuju manje određenog dobra jer ono raste u ceni. Stoga geometrijsko ponderisanje uzrokuje da roba sa velikim rastom cena ima manje uticaja na CPI, što dovodi do niže prijavljene inflacije.
Hedonika
Hedonika omogućava Birou za statistiku rada da menja cenu dobra na osnovu njegovog opaženog povećanja ‘korisnosti’ tokom vremena. Evo primera: recimo da se televizor sa rezolucijom od 720p 2009. godine prodavao za 200 USD. U 2010. godini isti model televizora sada ima rezoluciju od 1080p i prodaje se po istoj ceni: 200 USD. Međutim, pošto se tehnologija u televizoru poboljšala, zaposleni u Birou za statistiku rada mogu da izmisle ‘korisni’ broj i pomoću njega oduzmu deo vrednosti od cene televizora. Kao rezultat, BLS može da kaže da TV košta 180 USD u 2010. godini – iako je njegova cena 200 USD. Ovo dovodi do pada prijavljene inflacije.
Oba ova prilagođavanja smanjuju prijavljenu stopu inflacije, što smanjuje povećanje troškova života i isplate naknada za socijalno osiguranje. Koliko ta prilagođavanja inflacije pogađaju radničku klasu i penzionere? Neke procene, poput procena ekonomiste John Williams-a, sa koledža u Darmouthu, stavljaju stvarnu inflaciju u SAD na u proseku 3% – 6% više nego što je izveštavano od strane Bira za statistiku rada. To bi inflaciju u 2020 dovelo do 5% – 8%, umesto na prijavljenih 2%.
U 2021. godini prijavljena inflacija je 5.4%, u prvom kvartalu.
Da li inflacija pokreće ekonomski rast?
Mnogi ljudi veruju da stabilna inflacija pokreće ekonomski rast podstičući investicije i potrošnju umesto štednje. Međutim, osnovni ekonomski podaci pobijaju ovu uobičajenu tvrdnju.
Ako za primer uzmemo Sjedinjene Države, nacija je imala samo kratke periode inflacije od 1775. do oko 1950. godine, kao što pokazuje indeks potrošačkih cena koji je ostao nepromenjen. Inflacija dobija zamah tek nakon 1971. godine, pa bi bilo za očekivati da će i stopa rasta bruto domaćeg proizvoda (BDP) Sjedinjenih Država porasti nakon 1971. godine.
 Indeks potrošačkih cena, Sjedinjene Države, 1790-2015
Indeks potrošačkih cena, Sjedinjene Države, 1790-2015Međutim, vidimo da se bruto domaći proizvod (BDP) po stanovniku u Sjedinjenim Državama, uobičajena mera ekonomske snage, neprekidno povećavao od 1820. godine do danas po stopi od oko 1,85% godišnje. Ne postoji porast oko 1971. godine, uprkos rastućoj inflaciji koja je započela u to vreme.

Ovo je logaritamski grafikon, koji nam omogućava da bolje vizualizujemo rast tokom vremena: što više logaritamski grafikon podseća na pravu liniju, to je stopa promene konzistentnija. Za više detalja, ovde pogledajte naslov: Rast na tehnološkoj granici i rast dostizanja.
To pokazuje da inflacija ne pokreće ekonomski rast.
Nažalost, imamo dokaze da inflacija ima i druge neželjene posledice, poput nejednakosti bogatstva. Koncentracija bogatstva u top 1%, počela je da raste krajem 1970-ih, nekoliko godina nakon što su Sjedinjene Države skinule svet sa zlatnog standarda i pretvorile se u monetarni sistem zasnovan na dugovima koji zahteva monetarnu inflaciju, a time i inflaciju cena, da bi preživeo.
Za potpunu istoriju tranzicije novca sa robnog sistema na dužni sistem, pročitajte naš članak o novcu.
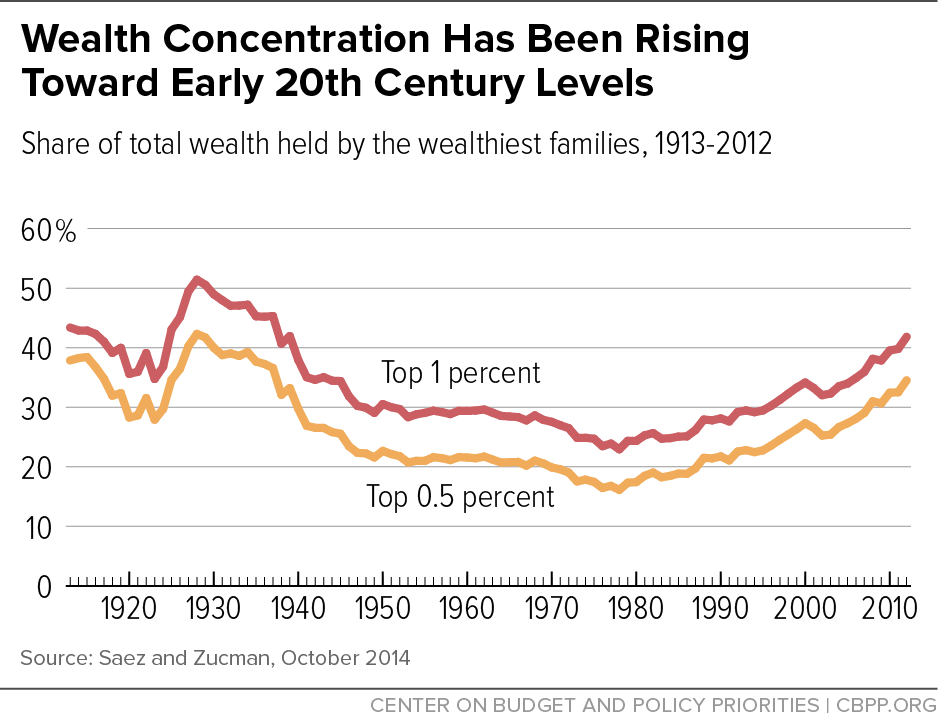
Da li inflacija pokreće ili umanjuje nejednakost bogatstva?
Veza između inflacije i nejednakosti bogatstva postaje jasna kada pogledamo kako novostvorena valuta ulazi u ekonomiju. Vlade, komercijalne banke, velike korporacije i bogati često koriste kredite da bi iskoristili prednosti svojih moći. Kada podignu kredite, oni novonastalu valutu dobijaju ranije od svih ostalih. Oni imaju koristi od inflacije trošenjem nove valute pre nego što cene počnu da rastu kao rezultat te nove valute koja kruži u ekonomiji. Veliki i bogati subjekti često mogu da dobiju kredite po nižim troškovima od prosečnog građanina ili malog preduzeća. To znači da mogu da povećaju svoje poslovanje i bogatstvo brže od manjih firmi.
Bogati mogu da dobiju jeftine zajmove, zahvaljujući Federalnim Rezervama koje zadržavaju niske kamatne stope. To im omogućava da koriste ovo prednost za ostvarivanje ogromne dobiti.
Inflacija pogadja one koji rade za platu i ne mogu da ulože veći deo svog prihoda. Zarade se polako menjaju, ponekad se uskladjuju samo jednom godišnje. Kao rezultat, cene osnovnih dobara i usluga često rastu mnogo pre nego što zarade porastu. Cena potrošačke korpe takođe se smanjuje sa manipulacijama indeksom potrošačkih cena (CPI) koji skriva rast inflacije.
Gde se danas javlja inflacija?
Rekordno visoka inflacija javlja se u zemljama kao što su Venecuela, Zimbabve, Turska, Iran, Kuba, Južna Afrika i Argentina. To dovodi do sloma trgovine i političke nestabilnosti.
U razvijenom svetu vlade izveštavaju o niskoj inflaciji cena. Međutim, globalni bankarski sistem stvara nove valute u tonama – u toku je velika monetarna inflacija. Centralne banke dovode do sve većeg stvaranja valuta snižavanjem kamatnih stopa. To dovodi do toga da korporacije i pojedinci mogu da uzimaju jeftinije kredite, a svaki kredit znači stvaranje nove valute. Od 2008. godine, gotovo sve glavne centralne banke postavile su kamatne stope blizu nule.
Mnoge centralne banke takođe su pozajmljivale ogromne iznose vladama i bankama koje su propale nakon finansijske krize 2008. godine. Za samo nekoliko meseci, ovo je udvostručilo (ponekad utrostručilo ili učetvorostručilo) novčanu masu mnogih nacija. Oni su ovo nazvali „kvantitativno ublažavanje“.
Ako banke koriste toliku monetarnu inflaciju, zašto onda mi ne vidimo inflaciju cena?
Jednostavno rečeno, većina nove valute nije dospela u ruke običnih ljudi. Kada obični ljudi budu mogli da potroše novoštampanu valutu na svoje svakodnevne potrebe, tada ćemo videti rast CPI i inflacije.
Danas većina valuta ulazi u svet putem bankarskih zajmova, pa banke igraju veliku ulogu u tome gde se dešava inflacija. Banke prvenstveno pozajmljuju vrlo ‘sigurnim’ klijentima poput bogatih pojedinaca, vlada i velikih korporacija. Ovi subjekti kupuju luksuznu robu, umetnička dela, finansijsku imovinu i državne obveznice.
Cene ovih vrsta imovine nisu uključene u CPI, tako da je prijavljena inflacija niska. Kao rezultat, povećanje plata i isplate socijalnog osiguranja su takođe na niskom nivou.
 Bogati su uživali u periodu od 2008. do 2021. godine, kada je njihova imovina upumpavana sa velikom količinom novog novca proizvedenog od bankarskih kredita!
Bogati su uživali u periodu od 2008. do 2021. godine, kada je njihova imovina upumpavana sa velikom količinom novog novca proizvedenog od bankarskih kredita!Šta se dešava kada nova valuta dodje u ruke običnih ljudi?
Nažalost, jednog dana će sva ova nova valuta da uđe u normalnu ekonomiju i time će se povećati cene svakodnevne robe. To je poćelo da se dešava 2021. godine kao rezultat stimulativnih programa COVID-19 u Sjedinjenim Državama, koji su ljudima distribuirali trilione dolara. Iako je ovo zasigurno poželjnije od spašavanja korporacija, svaka vrsta spašavanja koja uključuje štampanje novca ima gadne dugoročne efekte.
Ovo što sada doživljavamo dogodilo se u Nemačkoj tokom i posle Prvog svetskog rata. Cene u Nemačkoj su zapravo pale tokom Prvog svetskog rata uprkos velikom stvaranju valute od strane Nemačke centralne banke. Nisko poverenje u ekonomiju sprečavalo je nemački narod da troši novac. Međutim, kad se rat završio i kada su ljudi ponovo počeli da ga troše, cene su vrlo naglo skočile i valuta je postala bezvredna. To bi moglo da se dogodi 2020-ih u Sjedinjenim Državama, sa obzirom na predložene programe podsticaja.
Politike poput Univerzalnog Osnovnog Dohotka, eng. Universal Basic Income (UBI), koje izgledaju pogodne za njihova obećanja da će “spasiti ljude”, takođe mogu da pokrenu hiperinflaciju. Obični ljudi bi se osećali imućnije, trošili bi svoju novoštampanu valutu i doveli do brzog rasta cena. Ovo bi u suštini poništilo pozitivan uticaj građana koji dobijaju “besplatan novac” svakog meseca.
Pa kako onda vi možete da zaštitite svoju ušteđevinu od inflacije? Kupujte imovinu koja je retka, potcenjena i koju vlade teško mogu da prigrabe. Ova imovina su plemeniti metali poput zlata, i Bitcoin.
Šta je deflacija?
Deflacija znači pad cena tokom vremena. Mnogi ekonomisti kažu da će ovo dovesti do toga da ljudi gomilaju valutu i da će dovesti do ekonomskog kolapsa, jer ljudi prestaju da kupuju robu i ulažu u preduzeća. To jednostavno nije tačno, jer ljudi uvek imaju potrebe i želje zbog kojih kupuju odredjenu robu. Stalni pad cena tokom vremena jednostavno bi promenio psihologiju potrošačke kulture u kojoj živimo.
Potrošačka kultura potiče od inflacije
Kako je to istina? Pogledajmo na sledećem primeru. Recimo da želite novi auto i da imate dovoljno novca da ga kupite. Poznato je da u našem svetu zbog stalne inflacije vaš novac vremenom postaje sve manje i manje vredan. U paralelnom svemiru u kojem se javlja stalna deflacija, vaš novac vremenom postaje sve vredniji.
- Uz konstantnu inflaciju, auto će koštati nešto više sledeće godine, i nešto više naredne godine. Niste sigurni gde da uložite novac da biste sa vremenom sigurno očuvali njegovu kupovnu moć. Ako niste sigurni da li ćete da kupite auto, ima više finansijskog smisla da ga kupite odmah, da biste dobili najbolju ponudu.
- Uz konstantnu deflaciju, auto će koštati nešto manje sledeće, i još manje naredne godine. Ako samo čuvate vaš novac, sledeće godine ćete dobiti bolju ponudu za auto. Ako niste sigurni da li ćete da kupite auto, ima više finansijskog smisla da sačekate malo duže da biste dobili bolju ponudu.
Sada razmislite o ta dva scenarija, pomnožena bilionima ljudi i proizvoda. Uz konstantnu inflaciju, svako ima malo više razloga da kupuje stvari upravo sada. Uz konstantnu deflaciju, svi sada imaju malo manje razloga da kupuju. Upravo na taj način inflacija je u osnovi naše materijalističke, potrošačke kulture. Deflacija bi mogla da bude lek.
Inflacija uzrokuje loše investicije
Vaš novac godišnje gubi “2%” svoje vrednosti zbog inflacije. Sada, recimo da vas Stefan pita da investirate u njegov Fast food. Nakon uvida u brojeve, verujete da ćete ovom investicijom izgubiti 1% od vrednosti svog novca. Gubitak od 1% u Stefanovom poslu bolji je od gubitka od 2% zbog inflacije, pa se vi odlučujete da uložite. Ovo je loša investicija, eng. malinvestment – investirajući vi ćete da izgubite deo vrednosti. Međutim, čuvanje valute je još gore, zato ulažete.
Mnogi investitori, poput penzijskih fondova, danas su prisiljeni da investiraju u neprofitabilne biznise zbog investicionih mandata i same veličine njihove ‘imovine pod upravljanjem’.
Pristalice konstantno niske inflacije veruju da bi deflacija smanjila investicije. Međutim, to bi samo smanjilo ulaganje u preduzeća sa negativnim očekivanim prinosom poput Stefanovog Fast food-a. Na primer, recimo da je deflacija u proseku oko 2% godišnje. Na ovom tržištu investitori bi jednostavno prestali da ulažu u projekte za koje misle da će im zaraditi manje od 2% godišnjeg povrata ulaganja.
Neznatno deflaciona valuta obeshrabriće ulaganja u lažna i loša preduzeća i podstaći ulaganje u solidna preduzeća koja svetu dodaju vrednost.
Kakav uticaj inflacija ima na društvo?
Inflacija pokreće povećanu potrošnju, smanjenu štednju i povećani dug. Sve ove stvari dovode do toga da većina ljudi mora da radi više sati i duže u starosti. Iako inflacija kažnjava one koji rade za platu, ona obogaćuje vlasnike bilo koje imovine koja dobija na ceni kada nova valuta uđe u sistem. Ova imovina uključuje akcije, umetnička dela, nekretnine i drugu imovinu koju bogataši koriste za čuvanje svog bogatstva.
Vremenom ljudi i firme izmišljaju nove načine za jeftinije stvaranje dobara i usluga višeg kvaliteta. Ovo je poznato kao ‘rast produktivnosti’ i trebalo bi da uzrokuje da cene tokom vremena konstantno padaju, a ne da rastu. Samo konstantno stvaranje valute koje je neophodno zbog monetarnog sistema zasnovanog na dugu naše vlade uzrokuje stalnu inflaciju i njene loše efekte.
Ako vam se sviđa moj rad, molim vas da ga podelite sa svojim prijateljima i porodicom. Cilj mi je da svima pružim pogled u ekonomiju i na to kako ona utiče na njihov život.
-
 @ 86611181:9fc27ad7
2025-05-23 20:31:44
@ 86611181:9fc27ad7
2025-05-23 20:31:44It's time to secure user data in your identity system This post was also published with the Industry Association of Privacy Professionals.
It seems like every day there is a new report of a major personal data breach. In just the past few months, Neiman Marcus, Ticketmaster, Evolve Bank, TeamViewer, Hubspot, and even the IRS have been affected.
The core issue is that user data is commonly spread across multiple systems that are increasingly difficult to fully secure, including database user tables, data warehouses and unstructured documents.
Most enterprises are already running an incredibly secure and hardened identity system to manage customer login and authorization, commonly referred to as a customer identity access management system. Since identity systems manage customer sign-up and sign-in, they typically contain customer names, email addresses, and phone numbers for multifactor authentication. Commercial CIAMs provide extensive logging, threat detection, availability and patch management.
Identity systems are highly secure and already store customers' personally identifiable information, so it stands to reason enterprises should consider identity systems to manage additional PII fields.
Identity systems are designed to store numerous PII fields and mask the fields for other systems. The Liberty Project developed the protocols that became Security Assertion Markup Language 2.0, the architecture at the core of CIAM systems, 20 years ago, when I was its chief technology officer. SAML 2.0 was built so identity data would be fully secure, and opaque tokens would be shared with other systems. Using tokens instead of actual user data is a core feature of identity software that can be used to fully secure user data across applications.
Most modern identity systems support adding additional customer fields, so it is easy to add new fields like Social Security numbers and physical addresses. Almost like a database, some identity systems even support additional tables and images.
A great feature of identity systems is that they often provide a full suite of user interface components for users to register, login and manage their profile fields. Moving fields like Social Security numbers from your database to your identity system means the identity system can fully manage the process of users entering, viewing and editing the field, and your existing application and database become descoped from managing sensitive data.
With sensitive fields fully isolated in an identity system and its user interface components, the identity system can provide for cumbersome and expensive compliance with standards such as the Health Insurance Portability and Accountability Act for medical data and the Payment Card Industry Data Security Standard for payment data, saving the time and effort to achieve similar compliance in your application.
There are, of course, applications that require sensitive data, such as customer service systems and data warehouses. Identity systems use a data distribution standard called System for Cross-domain Identity Management 2.0 to copy user data to other systems. The SCIM is a great standard to help manage compliance such as "right to be forgotten," because it can automatically delete customer data from other systems when a customer record is deleted from the identity system.
When copying customer data from an identity system to another application, consider anonymizing or masking fields. For example, anonymizing a birthdate into an age range when copying a customer record into a data warehouse can descope the data warehouse from containing personal information.
Most enterprises already run an Application Programming Interface Gateway to manage web services between systems. By combining an API Gateway with the identity system's APIs, it becomes very easy to automatically anonymize and mask customer data fields before they are copied into other systems.
A new set of companies including Baffle, Skyflow, and Piiano have introduced services that combine the governance and field management features of an identity system with extensive field masking. Since these systems do not offer the authentication and authorization features of an identity system, it's important to balance the additional features as they introduce an additional threat surface with PII storage and permissions.
PII sprawl is an increasing liability for companies. The most secure, compliant and flexible central data store to manage PII is the existing CIAM and API Gateway infrastructure that enterprises have already deployed.
Move that customer data into your identity system and lock it down. https://peter.layer3.press/articles/3c6912eb-404a-4630-9fe9-fd1bd23cfa64
-
 @ 6d5c826a:4b27b659
2025-05-23 21:48:04
@ 6d5c826a:4b27b659
2025-05-23 21:48:04- GNS3 - Graphical network simulator that provides a variety of virtual appliances. (Source Code)
GPL-3.0Python - OpenWISP - Open Source Network Management System for OpenWRT based routers and access points. (Demo, Source Code)
GPL-3.0Python - Oxidized - Network device configuration backup tool.
Apache-2.0Ruby - phpIPAM - Open source IP address management with PowerDNS integration. (Source Code)
GPL-3.0PHP - RANCID - Monitor network devices configuration and maintain history of changes. (Source Code)
BSD-3-ClausePerl/Shell - rConfig - Network device configuration management tool. (Source Code)
GPL-3.0PHP
- GNS3 - Graphical network simulator that provides a variety of virtual appliances. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:47:44
@ 6d5c826a:4b27b659
2025-05-23 21:47:44- Adagios - Web based Nagios interface for configuration and monitoring (replacement to the standard interface), and a REST interface. (Source Code)
AGPL-3.0Docker/Python - Alerta - Distributed, scalable and flexible monitoring system. (Source Code)
Apache-2.0Python - Beszel - Lightweight server monitoring platform that includes Docker statistics, historical data, and alert functions. (Source Code)
MITGo - Cacti - Web-based network monitoring and graphing tool. (Source Code)
GPL-2.0PHP - cadvisor - Analyzes resource usage and performance characteristics of running containers.
Apache-2.0Go - checkmk - Comprehensive solution for monitoring of applications, servers, and networks. (Source Code)
GPL-2.0Python/PHP - dashdot - A simple, modern server dashboard for smaller private servers. (Demo)
MITNodejs/Docker - EdMon - A command-line monitoring application helping you to check that your hosts and services are available, with notifications support.
MITJava - eZ Server Monitor - A lightweight and simple dashboard monitor for Linux, available in Web and Bash application. (Source Code)
GPL-3.0PHP/Shell - glances - Open-source, cross-platform real-time monitoring tool with CLI and web dashboard interfaces and many exporting options. (Source Code)
GPL-3.0Python - Healthchecks - Monitoring for cron jobs, background services and scheduled tasks. (Source Code)
BSD-3-ClausePython - Icinga - Nagios fork that has since lapped nagios several times. Comes with the possibility of clustered monitoring. (Source Code)
GPL-2.0C++ - LibreNMS - Fully featured network monitoring system that provides a wealth of features and device support. (Source Code)
GPL-3.0PHP - Linux Dash - A low-overhead monitoring web dashboard for a GNU/Linux machine.
MITNodejs/Go/Python/PHP - Monit - Small utility for managing and monitoring Unix systems. (Source Code)
AGPL-3.0C - Munin - Networked resource monitoring tool. (Source Code)
GPL-2.0Perl/Shell - Naemon - Network monitoring tool based on the Nagios 4 core with performance enhancements and new features. (Source Code)
GPL-2.0C - Nagios - Computer system, network and infrastructure monitoring software application. (Source Code)
GPL-2.0C - Netdata - Distributed, real-time, performance and health monitoring for systems and applications. Runs on Linux, FreeBSD, and MacOS. (Source Code)
GPL-3.0C - NetXMS - Open Source network and infrastructure monitoring and management. (Source Code)
LGPL-3.0/GPL-3.0Java/C++/C - Observium Community Edition - Network monitoring and management platform that provides real-time insight into network health and performance.
QPL-1.0PHP - openITCOCKPIT Community Edition - Monitoring Suite featuring seamless integrations with Naemon, Checkmk, Grafana and more. (Demo, Source Code)
GPL-3.0deb/Docker - Performance Co-Pilot - Lightweight, distributed system performance and analysis framework. (Source Code)
LGPL-2.1/GPL-2.0C - PHP Server Monitor - Open source tool to monitor your servers and websites. (Source Code)
GPL-3.0PHP - PhpSysInfo - A customizable PHP script that displays information about your system nicely. (Source Code)
GPL-2.0PHP - Prometheus - Service monitoring system and time series database. (Source Code)
Apache-2.0Go - Riemann - Flexible and fast events processor allowing complex events/metrics analysis. (Source Code)
EPL-1.0Java - rtop - Interactive, remote system monitoring tool based on SSH.
MITGo - ruptime - Classic system status server.
AGPL-3.0Shell - Scrutiny - Web UI for hard drive S.M.A.R.T monitoring, historical trends & real-world failure thresholds.
MITGo - Sensu - Monitoring tool for ephemeral infrastructure and distributed applications. (Source Code)
MITGo - Status - Simple and lightweight system monitoring tool for small homeservers with a pleasant web interface. (Demo
MITPython - Thruk - Multibackend monitoring web interface with support for Naemon, Nagios, Icinga and Shinken. (Source Code)
GPL-1.0Perl - Wazuh - Unified XDR and SIEM protection for endpoints and cloud workloads. (Source Code)
GPL-2.0C - Zabbix - Enterprise-class software for monitoring of networks and applications. (Source Code)
GPL-2.0C
- Adagios - Web based Nagios interface for configuration and monitoring (replacement to the standard interface), and a REST interface. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:47:22
@ 6d5c826a:4b27b659
2025-05-23 21:47:22- Chocolatey - The package manager for Windows. (Source Code)
Apache-2.0C#/PowerShell - Clonezilla - Partition and disk imaging/cloning program. (Source Code)
GPL-2.0Perl/Shell/Other - DadaMail - Mailing List Manager, written in Perl. (Source Code)
GPL-2.0Perl - Fog - Cloning/imaging solution/rescue suite. (Source Code)
GPL-3.0PHP/Shell - phpList - Newsletter and email marketing software. (Source Code)
AGPL-3.0PHP
- Chocolatey - The package manager for Windows. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:47:03
@ 6d5c826a:4b27b659
2025-05-23 21:47:03- Beats - Single-purpose data shippers that send data from hundreds or thousands of machines and systems to Logstash or Elasticsearch. (Source Code)
Apache-2.0Go - Collectd - System statistics collection daemon. (Source Code)
MITC - Diamond - Daemon that collects system metrics and publishes them to Graphite (and others).
MITPython - Grafana - A Graphite & InfluxDB Dashboard and Graph Editor. (Source Code)
AGPL-3.0Go - Graphite - Scalable graphing server. (Source Code)
Apache-2.0Python - RRDtool - Industry standard, high performance data logging and graphing system for time series data. (Source Code)
GPL-2.0C - Statsd - Daemon that listens for statistics like counters and timers, sent over UDP or TCP, and sends aggregates to one or more pluggable backend services.
MITNodejs - tcollector - Gathers data from local collectors and pushes the data to OpenTSDB. (Source Code)
LGPL-3.0/GPL-3.0Python - Telegraf - Plugin-driven server agent for collecting, processing, aggregating, and writing metrics.
MITGo
- Beats - Single-purpose data shippers that send data from hundreds or thousands of machines and systems to Logstash or Elasticsearch. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:46:46
@ 6d5c826a:4b27b659
2025-05-23 21:46:46- aerc - Terminal MUA with a focus on plaintext and features for developers. (Source Code)
MITGo - Claws Mail - Old school email client (and news reader), based on GTK+. (Source Code)
GPL-3.0C - ImapSync - Simple IMAP migration tool for copying mailboxes to other servers. (Source Code)
NLPLPerl - Mutt - Small but very powerful text-based mail client. (Source Code)
GPL-2.0C - Sylpheed - Still developed predecessor to Claws Mail, lightweight mail client. (Source Code)
GPL-2.0C - Thunderbird - Free email application that's easy to set up and customize. (Source Code)
MPL-2.0C/C++
- aerc - Terminal MUA with a focus on plaintext and features for developers. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:46:28
@ 6d5c826a:4b27b659
2025-05-23 21:46:28- Fluentd - Data collector for unified logging layer. (Source Code)
Apache-2.0Ruby - Flume - Distributed, reliable, and available service for efficiently collecting, aggregating, and moving large amounts of log data. (Source Code)
Apache-2.0Java - GoAccess - Real-time web log analyzer and interactive viewer that runs in a terminal or through the browser. (Source Code)
MITC - Loki - Log aggregation system designed to store and query logs from all your applications and infrastructure. (Source Code)
AGPL-3.0Go - rsyslog - Rocket-fast system for log processing. (Source Code)
GPL-3.0C
- Fluentd - Data collector for unified logging layer. (Source Code)
-
 @ bf47c19e:c3d2573b
2025-05-23 20:25:36
@ bf47c19e:c3d2573b
2025-05-23 20:25:36Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Definisanje novca
- Šta je sredstvo razmene?
- Šta je obračunska jedinica?
- Šta je zaliha vrednosti?
- Zašto su važne funkcije novca?
- Novac Gubi Funkciju: Alhemičar iz Njutonije
- Eksploatacija pomoću Novca: Agri Perle
- Novac Gubi Funkciju 2. Deo: Kejnslandski Bankar
- Da li nas novac danas eksploatiše?
- Šta je novac, i zašto trebate da brinete?
- Efikasnija Ušteda Novca
- Zasluge
- Molim vas da šerujete!
Google izveštava o stalnom povećanju interesa u svetu za pitanje „Šta je novac?“ koji se postavlja iz godine u godinu, od 2004. do 2021., a sa naglim porastom nakon finansijske krize 2008. godine.
I izgleda se da niko nema dobar odgovor za to.
 Godišnji proseci mesečnih interesa za pretragu. 100 predstavlja najveći interes za pretragu tokom čitavog perioda, koji se dogodio u decembru 2019. Podaci sa Google Trends-a.
Godišnji proseci mesečnih interesa za pretragu. 100 predstavlja najveći interes za pretragu tokom čitavog perioda, koji se dogodio u decembru 2019. Podaci sa Google Trends-a.Međutim, odgovaranje na ovo naizgled jednostavno pitanje pomoći će vam da razjasnite ulogu novca u vašem životu. Jednom kada shvatite kako novac funkcioniše, tačno ćete videti i zašto svet danas ludi – i šta učiniti povodom toga. Zato hajde da se udubimo u to.
Na pitanje šta je novac, većina ljudi otvori svoje novčanike i pokaže nekoliko novčanica – “evo, ovo je novac!”
Ali po čemu se ove novčanice razlikuju od stranica vaše omiljene knjige? Pa, naravno, zavod za izradu novčanica te zemlje je odštampao te novčanice iz vašeg novčanika kako bi se oduprla falsifikovanju, i svi ih koriste da bi kupili odredjene stvari.
Međutim, Nemačka Marka imala je sva ova svojstva u prošlosti – ali preduzeća danas ne prihvataju te novčanice. Zapravo, građani Nemačke su početkom dvadesetih godina prošlog veka spaljivali papirne Marke kako bi grejali svoje domove. Marka je imala veću vrednost kao papir za potpalu nego kao novac!

1923. nemačka valuta poznata kao Marka bila je jeftinija od uglja i drveta!
Pa šta to čini novac, novcem?
Ispostavilo se da ovo nije pitanje na koje je lako dati odgovor.
Definisanje novca
Novac nije fizička stvar poput novčanice dolara. Novac je društveni sistem koji koristimo da bismo olakšali trgovinu robom i uslugama. Međutim, tokom istorije fizička monetarna dobra igrala su ključnu ulogu u društvenom sistemu novca, često kao znakovi koji predstavljaju vrednost u monetarnom sistemu. Ovaj sistem ima tri funkcije: 1) Sredstvo Razmene, 2) Obračunsku Jedinicu i 3) Zalihu Vrednosti.
Odakle dolaze ove funkcije, i zašto su one vredne?
Šta je sredstvo razmene?
Sredstvo razmene je neko dobro koje se obično razmenjuje za drugo dobro. Najčešće objašnjenje za to kako su se pojavila sredstva razmene glasi otprilike ovako: Boris ima ječam i želeo bi da kupi ovcu od Marka. Marko ima ovce, ali želi samo piliće. Ana ima piliće, ali ona ne želi ječam ili ovce.
To se naziva problem sticaja potreba: dve strane moraju da žele ono što druga ima da bi mogle da trguju. Ako se želje dve osobe ne podudaraju, oni moraju da pronađu druge ljude sa kojima će trgovati dok svi ne pronađu dobro koje žele.
 Ljudi koji trguju robom i uslugama moraju da imaju potrebe koje se podudaraju.
Ljudi koji trguju robom i uslugama moraju da imaju potrebe koje se podudaraju.Vremenom, veoma je verovatno da će se određena vrsta robe, poput pšenice, pojaviti kao sredstvo razmene jer su je mnogi ljudi želeli. Uzimajući pšenicu kao primer: pšenica je rešila “sticaje potreba” u mnogim zanatima, jer čak i ako onaj koji prima pšenicu a nije želeo da je koristi za sebe, znao je da će je neko drugi želeti.
Ovo nazivamo prodajnost imovine.
Pšenica je dobar primer dobra za prodaju jer svi moraju da jedu, a od pšenice se pravi hleb. Pšenica ima vrednost kao sastojak hleba i kao dobro koje olakšava trgovinu rešavanjem problema „sticaja potreba“.
Razmislite o svojoj želji da dobijete više novčanica u eurima ili drugoj valuti. Ne možete da jedete novčanice da biste preživeli, a i ne bi vam bile od velike koristi ako poželite da ih koristite kao građevinski materijal za vašu kuću. Međutim, znate da sa tim novčanicama možete da kupite hranu i kuću.
Stvarne fizičke novčanice su beskorisne za vas. Novčanice su vam dragocene samo zato što će ih drugi prihvatiti za stvari koje su vama korisne.
Tokom dugog perioda istorije, novac je evoluirao do te mere da monetarno dobro može imati vrednost, a da to dobro ne služi za bilo koju drugu ‘suštinsku’ upotrebu, poput hrane ili energije. Umesto toga, njegova upotreba je zaliha vrednosti i jednostavna zamena za drugu robu u bilo kom trenutku koji poželite.
Šta jedno dobro čini poželjnijim i prodajnijim od drugog dobra?
Deljivost
Definicija: Sposobnost podele dobra na manje količine.
Loš Primer: Dijamante je teško podeliti na manje komade. Za zajednicu od hiljada ljudi koji dnevno izvrše milione transakcija, dijamanti čine loše sredstvo razmene. Previše su retki i nedeljivi da bi se koristili za mnoge transakcije.
 Potrebno je puno obuke da bi izrezali dijamant.
Potrebno je puno obuke da bi izrezali dijamant.Ujednačenost
Definicija: Sličnost pojedinačnih jedinica odredjenog dobra.
Loš Primer: Krave nisu ujednačene – neke su veće, neke manje, neke bolesne, neke zdrave. Sa druge strane, unca čistog zlata je jednolična – jedna unca je potpuno ista kao sledeća. Ovo svojstvo se takođe često naziva zamenljivost.
 Svaka je jedinstvena na svoj način.
Svaka je jedinstvena na svoj način.Prenosivost
Definicija: Lakoća transporta dobra.
Loš Primer: Krava nije baš prenosiva. Zlatnici su prilično prenosivi. Papirne novčanice su još prenošljivije. Knjiga u kojoj se jednostavno beleži vlasništvo nad tim vrednostima (poput Rai kamenog sistema ili digitalnog bankovnog računa) je neverovatno prenosiva, jer nema fizičkog dobra koje treba nositi sa sobom za kupovinu. Postoji samo sistem za evidentiranje vlasništva nad tim vrednostima u nematerijalnom obliku.
 Novac star 5000 godina VS novac star 13 godina
Novac star 5000 godina VS novac star 13 godinaKako dobro postaje sredstvo razmene?
Dobra postaju, i ostaju sredstva razmene zbog svoje univerzalne potražnje, takođe poznate kao njihova prodajnost, čemu pomažu svojstva koja su gore nabrojana.
Mnogo različitih dobara mogu u različitoj meri delovati kao sredstva razmene u ekonomiji. Danas, naša globalna ekonomija koristi valute koje izdaju države, zlato, pa čak i robu poput nafte kao sredstvo razmene.
Šta je obračunska jedinica?
Stvari se komplikuju kada u ekonomiji postoji mnogo robe koja se prodaje. Čak i sa samo 5 dobara, postoji 10 “kurseva razmene” između svake robe kojih svi u ekonomiji moraju da se sete: 1 svinja se menja za 15 pilića, 1 pile se menja za 15 litara mleka, desetak jaja se menja za 15 litara mleka, i tako dalje. Ako ekonomija ima 50 dobara, među njima postoji 1.225 “kurseva razmene”!
Sredstvo za merenje vrednosti
Zamislite obračunsku jedinicu kao sredstvo za merenje vrednosti. Umesto da se sećamo vrednosti svakog dobra u poredjenju sa drugim dobrima, mi samo treba da se setimo vrednosti svakog dobra u poredjenju sa jednim dobrom – obračunskom jedinicom.
Umesto da se setimo 1.225 kurseva razmene kada imamo 50 proizvoda na tržištu, mi treba da zapamtimo samo 50 cena.
Na primer, ne treba da se sećamo da litar mleka vredi 1/15 piletine ili desetak jaja, možemo da se samo setimo da litar mleka košta 1USD.
 Mnogo opcija, sve u istoj obračunskoj jedinici.
Mnogo opcija, sve u istoj obračunskoj jedinici.Poređenje dobara je lakše sa obračunskom jedinicom
Obračunska jedinica takođe olakšava upoređivanje vrednosti i donošenje odluka. Zamislite da pokušavate da kupite par Nike Air Jordan patika kada ih jedan prodavac prodaje za jedno pile, a drugi za 50 klipova kukuruza.
Šta je zaliha vrednosti?
Do sada smo gledali samo primere transakcija koje se odvijaju u određenom trenutku u vremenu.
Međutim, ljudi vrše transakcije tokom vremena – oni štede novac i troše ga kasnije. Da bi odredjeno dobro moglo da funkcioniše pravilno kao monetarno dobro, ono treba da održi vrednost tokom vremena.
Novac koji vremenom dobro drži vrednost daje njegovom imaocu više izbora kada će taj novac da potroši.
To znači da prodajnost dobra uključuje njegovu sposobnost da održi vrednost tokom vremena.
Šta jedno dobro čini boljom zalihom vrednosti od drugog dobra?
Trajnost
Definicija: Sposobnost dobra da vremenom zadrži svoj oblik.
Loš Primer: Jagode čine lošu zalihu vrednosti jer se lako oštete i brzo trunu.
Odluka je daleko lakša ako jedan prodavac naplaćuje 150 USD, a drugi 200 USD – odmah je očigledno koja je bolja ponuda jer su vrednosti izražene u istoj jedinici.
 Nije sjajna forma novca.
Nije sjajna forma novca.Teške za Proizvodnju
Definicija: Teškoće koje ljudi imaju u proizvodnji veće količine dobra.
Loš Primer: Papirne novčanice predstavljaju lošu zalihu vrednosti jer banke i vlade mogu jeftino da ih naprave.
Sa zlatom je suprotno – u ponudi se nalazi ograničena količina uprkos velikoj potražnji za njim, jednostavno zato što ga je vrlo teško iskopati iz zemlje. Ova ograničena ponuda osigurava da svaka jedinica zlata održi vrednost tokom vremena.
 Traženje zlata je spora i teška aktivnost. Obično se ne pronađe puno!
Traženje zlata je spora i teška aktivnost. Obično se ne pronađe puno!Kako dobra postaju zalihe vrednosti?
Dobro postaje zaliha vrednosti ako se vremenom pokaže trajnim i teškim za proizvodnju.
Samo će vreme pokazati da li je neko dobro zaista trajno i da li ga je teško proizvesti. Zbog toga neki oblici novca su postojali vekovima pre nego što je neko otkrio način da ih proizvede više, i na kraju se to dobro više nije koristilo kao novac.
Ovo je priča o školjkama, Rai kamenju i mnogim drugim oblicima novca tokom istorije.
Zlato je primer dobra koje je hiljadama godina služilo kao dobra zaliha vrednosti. Zlato se ne razgrađuje tokom vremena i još uvek ga je teško proizvesti. Hiljadama godina alhemičari su bezuspešno pokušavali da sintetišu zlato iz jeftinih materijala.
Čak i sa današnjim naprednim rudarskim tehnikama, svake godine svi svetski rudnici zlata zajedno mogu da proizvedu samo 2% od ukupne ponude zlata u prometu.
Teškoće u proizvodnji zlata daju izuzetno visok odnos “zaliha i protoka”: zaliha je broj postojećih jedinica, a protok su nove jedinice stvorene tokom određenog vremenskog perioda. Svake godine se stvori vrlo malo novih jedinica zlata, iako je potražnja za zlatom obično vrlo velika.
Kombinujući ovo sa deljivošću, ujednačenošću i prenosivošću zlata, nije ni čudo što je zlato čovečanstvu služilo kao monetarno dobro tokom poslednjih 5.000 godina. Pošto je zlato teško proizvesti, možemo ga nazvati teškim novcem (hard money).
Kao rezultat toga, svoju vrednost je u velikoj meri zadržao kroz milenijume. Cena većine dobara i usluga u pogledu zlata zapravo se vremenom smanjivala kao rezultat tehnoloških inovacija, koje sve proizvode čine jeftinijim.
Uzmimo na primer cene hrane prema praćenju Kancelarije za hranu i poljoprivredu UN-a: sa obzirom na skokove u poljoprivrednoj tehnologiji tokom poslednjih 60 godina, cene hrane drastično su pale kada se procenjuju u zlatu. To čak i važi uprkos činjenici da obični ljudi retko koriste zlato za kupovinu stvari.
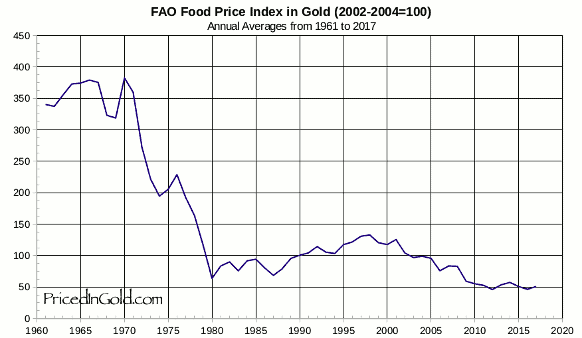 Cene hrane su padale u pogledu zlata tokom proteklih 60 godina, i mnogo pre toga (FAO Indeks Cena Hrane u Zlatu)
Cene hrane su padale u pogledu zlata tokom proteklih 60 godina, i mnogo pre toga (FAO Indeks Cena Hrane u Zlatu)Zaliha vrednosti omogućava ljudima da uštede novac kako bi mogli da ga ulažu u pokretanje preduzeća i obrazovanje, povećavajući produktivnost društva.
Monetarna dobra koja dobro čuvaju vrednost takođe podstiču dugoročniji pogled na život, ili kratke vremenske preference. Pojedinac može da radi 10 godina, uštedi odredjeno monetarno dobro koje je dobra zaliha vrednosti, i nema potrebe da se plaši da će njegova ušteđevina biti izbrisana krahom tržišta ili povećanjem ponude tog dobra.
Zašto su važne funkcije novca?
Kada neki oblik novca izgubi bilo koju od svojih važnih funkcija kao što su sredstvo razmene, obračunska jedinica i zaliha vrednosti, celokupna ekonomija i društvo mogu da se rastrgnu.
Tokom istorije često vidimo grupe ljudi koje eksploatišu druge iskorišćavajući nesporazume o novcu i važnosti njegovih funkcija.
Sledeće, proći ću kroz istoriju novca, prvo hipotetički da bih ilustrovao poentu, a zatim ću preći na stvarne istorijske primere. Kroz ove primere videćemo štetne efekte na društva u slučajevima kada se izgubi samo jedna od tih ključnih funkcija novca.
Novac Gubi Funkciju: Alhemičar iz Njutonije
Kroz istoriju, mnoga dobra su dolazila i odlazila kao oblici novca. Na žalost, kada se neki oblik novca ukine, ponekad postoji grupa ljudi koja eksploatiše drugi oblik manipulišući tim novcem.
Hajde da pogledamo hipotetičko selo zvano Njutonija da bismo razumeli kako dolazi do ove eksploatacije.
Zelene perle postaju Novac
Tokom stotina godina ribolova u obližnjoj reci, stanovnici Njutonije sakupljali su zelene perle iz vode. Zrnca su mala, lagana, izdržljiva, jednolična i retko se pojavljuju u reci. Ljudi prvo priželjkuju perle zbog svoje lepote. Na kraju, seljani shvataju da svi drugi žele perle – one se vrlo lako mogu prodati. Zrnca uskoro postaju sredstvo razmene i obračunska jedinica u selu: pile je 5 zrna, vreća jabuka 2 zrna, krava 80 zrna.
Ukupna ponuda perli je prilično konstantna i cene se vremenom ne menjaju mnogo. Seoski starešina je uveren da može da se opustiti u poslednjim danima živeći od svoje velike zalihe perli.
Alhemičar stvara više perli
Seoski alhemičar je poželeo da bude bogat čovek, ali nije voleo da vredno radi na tome. Umesto da traži perle u reci ili da prodaje vrednu robu drugim seljanima, on sedeo je u svojoj laboratoriji. Na kraju je otkrio kako da lako stvori stotine perli sa malo peska i vatre.
Seljani koji su tragali za perlama u reci bili su srećni ako bi svaki dan pronašli po 1 zrno. Alhemičar je mogao da proizvede stotine uz malo napora.
Alhemičar troši svoje perle
Budući da je bio prilično zao, alhemičar nije svoj metod pravljenja zrna delio ni sa kim drugim. Stvorio je sebi još više perli i počeo da ih troši za dobra na tržištu u Njutoniji. Tokom sledećih meseci, alhemičar je kupio farmu pilića, nekoliko krava, finu svilu, posteljine i ogromno imanje. On je imao priliku da kupi ova dobra po normalnim cenama na tržištu.
Alhemičarevo trošenje ostavljalo je seljanima mnogo perli, ali malo njihove vredne robe.
Svi seljani su se osećali bogatima – imali su tone perli! Međutim, polako su primetili da i svi ostali takodje imaju tone.
Cene počinju da rastu
Uzgajivač pilića primetio je da sva roba koju je trebalo da kupi na pijaci poskupela. Džak jabuka sada se prodaje za 100 perli – 50 puta više od njihove cene pre nekoliko meseci!
Iako je sada imao hiljade perli, uskoro bi mogao da ostane bez njih zbog ovih cena. Pitao se – da li zaista može sebi da priušti da prodaje svoje piliće za samo 5 perli po komadu? Morao je i on da podigne svoje cene.
Jednostavno rečeno, kao rezultat alhemičarevog trošenja njegovih novostvorenih perli, bilo je previše perli koje su jurile premalo dobara – pa su cene porasle.
Kupci robe bili su spremni da potroše više perli da bi kupili potrebna dobra. Prodavci robe su trebali da naplate više da bi bili sigurni da su zaradili dovoljno da kupe potrebna dobra za sebe.
Budući da su cene svih dobara porasle, možemo reći da se vrednost svake perle smanjila.
Nejednakost bogatstva raste
Seoski starešina, koji je vredno radio da sačuva hiljade perli, sada se našao osiromašenim i gladnim. U međuvremenu, alhemičar je udobno sedeo na svom velikom imanju sa kravama, pilićima i slugama koji su se brinuli za svaki njegov hir.
Alhemičar je efikasno ukrao bogatstvo celog sela, tako što je jeftino proizvodio perle i koristio ih za kupovinu vredne robe.
Ono što je najvažnije, kupio je robu pre nego što je tržište shvatilo da je više perli u opticaju i da ima manje robe, što je dovelo do rasta cena. Ova dodatna proizvodnja perli nije dodala korisnu robu ili usluge selu.
Eksploatacija pomoću Novca: Agri Perle
Nažalost, priča o alhemičaru iz Njutonije nije u potpunosti hipotetička. Ovaj prenos bogatstva kroz stvaranje novca ima istorijske i moderne presedane.
Na primer, afrička plemena su nekada koristila staklene perle, poznate kao “agri perle”, kao sredstvo razmene. U to vreme plemenskim ljudima je bilo veoma teško da prave staklene perle, i one su predstavljale težak novac unutar njihovog plemenskog društva.
Niko nije mogao jeftino da proizvede perle i koristiti ih za kupovinu skupe, vredne robe poput kuća, hrane i odeće.
 Perle proizvedene u Gani
Perle proizvedene u GaniSve se promenilo kada su stigli Evropljani, i primetili upotrebu staklenih perli kao novca.
U to vreme, Evropljani su mogli jeftino da stvaraju staklo u velikim količinama. Kao rezultat toga, Evropljani su počeli tajno da uvoze perle i koriste ih za kupovinu dobara, usluga i robova od Afrikanaca.
 Peć za izradu stakla u Muranu, Italija. Ovo ostrvo izvan Venecije proizvodi staklo od 15. veka.
Peć za izradu stakla u Muranu, Italija. Ovo ostrvo izvan Venecije proizvodi staklo od 15. veka.Vremenom se iz Afrike izvlačila vredna roba i ljudi, dok je plemenima ostajalo mnogo perli i malo robe.
Perle su izgubile veći deo vrednosti zbog inflacije uzrokovane snabdevanjem od strane Evropljana.
Rezultat je bio osiromašenje afričkih plemena i bogaćenje Evropljana, kako to ovde objašnjava monetarni istoričar Bezant Denier.
Dragocena roba je kupljena jeftino proizvedenim monetarnim dobrom.
Profitiranje na proizvodnji novca: Emisiona dobit
Ova priča ilustruje kako se bogatstvo prenosi kada jedna grupa može jeftino da proizvodi monetarno dobro.
Razlika između troškova proizvodnje monetarnog dobra i vrednosti tog monetarnog dobra poznata je kao emisiona dobit, eng. seignorage.
Kada je monetarno dobro mnogo vrednije od troškova proizvodnje, ljudi će proizvesti više od monetarnog dobra da bi uhvatili profit od emisione dobiti.
Na kraju će ova povećana ponuda dovesti do pada vrednosti monetarnog dobra. To je zbog zakona ponude i potražnje: kada se ponuda povećava, cena (poznata i kao vrednost) dobra opada.
Novac Gubi Funkciju 2. Deo: Kejnslandski Bankar
U priči o Njutoniji, alhemičar je otkrio način da se od malo peska jeftino stvori više zelenih perli. To se u stvarnosti odigralo kroz trgovinu između Evropljana i Afrikanaca, pričom o agri perlama. Međutim, ove priče su pomalo zastarele – mi više ne trgujemo robom za perle.
Da bismo nas doveli do modernog doba, hajde da promenimo neka imena u našoj priči:
- Selo Njutonija postaje država koja se zove Kejnsland
- Alhemičar postaje bankar
- Seoski starešina postaje penzioner
- Zelene perle postaju zlato, koje niko ne može jeftinije da stvori – čak ni bankar.
Bankar Menja Papirne Novčanice za Zlato
Kao i u stvarnosti, bankar u ovoj priči nema formulu ili trik da stvori više zlata. Međutim, bankar bezbedno čuva zlato u vlasništvu svakog građanina Kejnslanda. Bankar daje svakom građaninu po jednu potvrdu za svaku uncu zlata koje ima u svom trezoru.
Te potvrde se mogu iskoristiti u bilo koje vreme za stvarno zlato. Papirne potvrde ili novčanice su mnogo pogodnije za plaćanje nego nošenje zlata kroz supermarket.
Građani su srećni – oni imaju prikladno sredstvo plaćanja u vidu bankarevih novčanica, i znaju da niko ne može da ukrade njihovo bogatstvo falsifikujući više zlata.
Građani na kraju počinju da plaćaju u potpunosti papirnim novčanicama, ne trudeći se nikad da zamene svoje novčanice za zlato. Na kraju, novčanice postaju “dobre kao i zlato” – svaka predstavlja fiksnu količinu zlata u bankarevom trezoru.
Ukupno kruži 1.000.000 novčanica, od kojih je svaka otkupljiva za jednu uncu zlata. 1.000.000 unci zlata sedi u bankarevom trezoru. Svaka novčanica je u potpunosti podržana u zlatu.
Starešina koji je sačuvao sve svoje perle u priči o Njutoniji sada je penzioner u Kejnslandu, koji svoje zlato drži u banci i planira da ugodno živi od novčanica koje je dobio zauzvrat.
Hajde da u ovu priču dodamo i novi lik: premijera Kejnslanda. Premijer naplaćuje porez od građana i koristi ga za plaćanje javnih usluga poput policije i vojske. Premijer takođe drži vladino zlato kod bankara.
Bankar Menja Papirne Novčanice za Dug
Premijer želi da osigura da nacionalno zlato ostane na sigurnom, pa banku štiti policijom. Bankar i premijer se zbog toga zbližavaju, pa premijer traži uslugu. Traži od bankara da kreira 200.000 novčanica za premijera, uz obećanje da će mu premijer vratiti za pet godina. Premijeru su novčanice potrebne za finansiranje rata. Građani Kejnslanda borili su se protiv većih poreza zbog finansiranja rata, pa je morao da se obrati bankaru.
Bankar se slaže da izradi novčanice, ali pod jednim uslovom: bankar uzima deo od 10.000 novčanica za sebe. Premijer prihvata posao kojim bankar ’kupuje državni dug’. Sada je u opticaju 1.200.000 novčanica, potpomognutih kombinacijom 1.000.000 unci zlata i ugovorom o dugu sa vladom za 200.000 novčanica.
Premijer troši svoje nove novčanice na bombe kupujući ih od dobavljača iz domaće vojne industrije, a bankar sebi kupuje veliki luksuzni stan.
Dobavljač iz vojne industrije koristi sve nove novčanice koje je dobio od premijera da kupi amonijum nitrat (đubrivo koje se koristi u bombama) za proizvodnju bombi. Sve njegove kupovine povećavaju cenu đubriva za uzgajivače pšenice u Kejnslandu, pa oni podižu cenu pšenice.
Kao uzrok toga, pekar koji kupuje pšenicu treba da podigne cenu svog hleba da bi ostao u poslu. Na taj način cene u Kejnslandu počinju da rastu, baš kao što su to činile u Njutoniji kada su nove perle ušle u opticaj.
Papirne Novčanice Više Ne Predstavljaju Zlato
Penzioner nailazi na finansijski časopis u kojem se pominje premijerov dogovor da se zaduži za finansiranje rata. Obzirom da je mudar, on zna da bombe loše vraćaju ulaganje i sumnja da će premijer ikada da vrati svoj dug.
Ako on ‘podmiri’ svoj dug, to bi ostavilo 1.200.000 novčanica u opticaju sa samo 1.000.000 unci zlata da bi ih podržalo, obezvređujući njegovu ušteđevinu. Već oseća stisak u džepu zbog porasta cena, i on odlučuje da se uputi u lokalnu banku i preda svoje novčanice i zameni ih za zlato, koje niko ne može da napravi u većoj količini.
Kada penzioner stigne u banku, on zatiče i mnoge druge okupljene oko banke. Svi oni se nadaju da će uzeti zlato koje predstavljaju njihove novčanice. Građani Kejnslanda sa pravom se plaše da njihove novčanice gube na vrednosti – oni to već osećaju zbog porasta cena.
Vrata su zaključana, sa obaveštenjem bankara na njima:
Po nalogu premijera, onom koji se plaši za stabilnost ove bankarske institucije, ova banka više neće podržavati konvertibilnost papirnih novčanica u zlato. Hvala vam!
Gomila se razilazi, ostavljena sa jednim izborom: da zadrže svoje novčanice, koje sada vrede manje od 1 unce zlata. Građani sa dovoljno finansijske stabilnosti odlučuju da ulože svoje novčanice u kupovinu akcija banke i kompanija vojne industrije, koje dobro posluju jer mogu da kupuju stvari pre nego što se povećaju tržišne cene.
Mnogi ljudi nisu u mogućnosti da investiraju – oni moraju da gledaju kako njihove zarade stagniraju i kako njihova ušteđevina polako ali sigurno gubi vrednost.
Penzioner, koji se nadao da će živeti od novčanica koje je zaradio tokom svojih 40 radnih godina, sada 40 sati nedeljno provodi iza kase u lokalnoj prodavnici, pitajući se gde je sve pošlo po zlu.
Dug Nikada Nije Otplaćen
Prošlo je nekoliko godina, a premijerov dug prema banci dolazi na naplatu. Budući da je potrošio svih 200.000 novčanica na bombe, koje nemaju baš dobar povraćaj ulaganja, on nema novčanice koje može da vrati banci. Plus, premijer želi da kupi još bombi za svoj rat.
Bankar uverava premijera da je sve u redu. Bankar će napraviti novi ugovor o dugu za 600.000 novčanica, koji bi trebao da stigne na naplatu u narednih 5 godina. Premijer može da iskoristi 200.000 od tih novih 600.000 novčanica da vrati svoj prvobitni dug prema banci, zadrži još 300.000 da kupi još bombi i da 100.000 bankaru da bi mu platio njegove usluge.
To nastavlja da se dešava – svaki put kada dug dospeva na naplatu, bankar stvara više novčanica za vraćanje starijih dugova i daje premijeru još više novca za trošenje. Ovaj ciklus se nastavlja.
Šta se dešava u Kejnslandu?
- Oni koji prvi dobiju nove novčanice, gledaju kako se njihovo bogatstvo povećava
- To uključuje bankara, premijera, vladu i sve one koji mogu da pristupe mogućnostima za investiranje u preduzeća koja prva dobiju nove novčanice (finansijske, vojne itd.).
- Cene roba rastu
- Cene se ne povećavaju ravnomerno – one se povećavaju gde god nove novčanice prvo uđu u ekonomiju i od tog trenutka imaju efekat talasa na tržišta. U našem primeru prvo raste cena amonijum nitrata, zatim cena pšenice, pa cena hleba. A tek na kraju zarade običnih ljudi.
- Štednja i životni standard opšte populacije se smanjuju
- Najviše pate oni koji žive od plate do plate i ne mogu da ulažu. Čak i oni koji su u mogućnosti da investiraju podložni su hirovima tržišta. Mnogi su prisiljeni da prodaju svoje investicije po niskim cenama tokom pada tržišta samo da bi platili svoje dnevne potrebe.
- Razlika u prihodima i bogatstvu između bogatih i siromašnih se povećava
- Bogatstvo opšte populacije se smanjuje, dok se bogatstvo onih koji su blizu mesta gde se troše nove novčanice povećava. Rezultat je disparitet koji se vremenom samo proširuje.
Da li nas novac danas eksploatiše?
Priča o Njutoniji i stvarna priča o agri perlama u Africi deluju pomalo zastarelo. Priča o Kejnslandu, međutim, deluje neobično poznato. U našem svetu cene robe uvek rastu, i vidimo rekordne nivoe nejednakosti u bogatstvu.
U poslednjem odeljku ovog našeg članka Šta je novac, proći ću kroz nastanak bankarstva i korake koji su bili potrebni da se dođe do današnjeg sistema, gde banke i vlade sarađuju u kontroli ekonomije i samog novca.
Šta su banke, i odakle su one došle?
Pojava bankarstva verovatno se dogodila da bi olakšala poljoprivrednu trgovinu i da bi povećala pogodnosti. Iako su se mnoga društva na kraju konvergirala ka upotrebi zlata i srebra kao novca, ovi metali su bili teški i opasni za nošenje kao tovar. Međutim, u mnogim slučajevima ih nije ni trebalo prevoziti. Uzmite ovaj primer:
Grad treba da plati poljoprivrednicima na selu za žito, a poljoprivrednici gradskoj vojsci za zaštitu od varvara. U ovom dogovoru zlato se kreće u oba smera: prema poljoprivrednicima u selu kako bi im se platilo žito, i nazad u grad da bi se platila vojska. Da bi olakšali ove transakcije, preduzetnici su stvorili koncept banke. Banka je zlato čuvala u sigurnom trezoru i izdavala novčanice od papira. Svaka priznanica je predstavljala potvrdu da njen imaoc poseduje određenu količinu zlata u banci. Imaoc novčanice je u svako doba mogao da uzme svoje zlato nazad vraćanjem te novčanice banci.
Korisnici banke mogli su lakše da trguju sa novčanicama od papira, i onaj koji poseduje novčanice mogao je da preuzme njihovo fizičko zlato u bilo kom trenutku. To je te novčanice učinilo “dobrim kao i zlato”.
Banke su izdržavale svoje poslovanje naplaćujući od kupaca naknadu za skladištenje zlata ili pozajmljivanjem dela zlata i zaračunavanjem kamata na njega. Trgovina na ovaj način je mogla da se odvija sa laganim novčanicama od papira umesto sa teškim vrećama zlatnika.
Ovakva praksa sa transakcijama, korišćenjem papirne valute potpomognute monetarnim dobrima, verovatno je započela u Kini u 7. veku.
Na kraju se proširila Evropom 1600-ih, a svoj zalet dobila je u Holandiji sa bankama poput Amsterdamske Wisselbanke. Novčanice Wisselbank-e često su vredele više od zlata koje ih je podržavalo, zbog dodane vrednosti njihovih pogodnosti.
Uspon nacionalnih ‘centralnih banaka’
Tokom vekova, zlato je počelo da se sakuplja u trezorima banaka, jer su ljudi više voleli pogodnosti transakcija sa novčanicama.
Na kraju, nacionalne banke u vlasništvu vlada preuzele su ulogu čuvanja zlata od privatnih banaka koje su započeli preduzetnici.
Nacionalne papirne valute potpomognute zlatnim rezervama u nacionalnim bankama zamenile su novčanice iz privatnih banaka. Sve nacionalne valute bile su jednostavno potvrde za zlato koje se nalazilo u trezoru nacionalne banke.
Ovaj sistem je poznat kao zlatni standard – sve valute su jednostavno predstavljale različite težine zlata.
 U gornjem levom uglu novčanice možete videti da piše da je novčanica “zamenljiva za zlato”. Savremeni dolari nemaju ovaj natpis, ali inače izgledaju vrlo slično. Izvor
U gornjem levom uglu novčanice možete videti da piše da je novčanica “zamenljiva za zlato”. Savremeni dolari nemaju ovaj natpis, ali inače izgledaju vrlo slično. IzvorZlatni sistem je postojao veći deo vremena, sve do Prvog svetskog rata. Vladama je bilo teško da prikupe novac za ovaj rat putem poreza, pa su morale da budu kreativne.
Kada vlade troše više nego što zarađuju na porezima, to se naziva deficitna potrošnja.
Kako vlade mogu ovo da urade? Vlade to rade tako što pozajmljuju novac prodavajući svoj dug.
Tokom Prvog svetskog rata, vlade su građanima i preduzećima prodavale vrstu duga koja se naziva ratna obveznica. Kada građanin kupi ratnu obveznicu, on preda svoj novac vladi i dobije papir u kojem je stajalo vladino obećanje da će vlasniku obveznice vratiti novac, plus kamate, za nekoliko godina.
 Plakat koji obaveštava građane, tražeći od njih da kupe ratne obveznice – što predstavlja zajam vladi. Izvor
Plakat koji obaveštava građane, tražeći od njih da kupe ratne obveznice – što predstavlja zajam vladi. IzvorCentralne banke ‘monetizuju’ državni dug
Međutim, građani i preduzeća nisu bili voljni da kupe dovoljno ratnih obveznica za finansiranje Prvog svetskog rata.
Vlade se nisu predale – pa su zatražile od svojih nacionalnih ‘centralnih banaka’ da one kupe ove obveznice. Centralne banke su otkupile obveznice, ali ih nisu platile valutom potpomognutom postojećim zlatnim rezervama, kao što su to činili građani i banke prilikom kupovine obveznica.
Centralne banke su umesto toga davale vladi novu, sveže štampanu papirnu valutu potpomognutu samo obveznicom. Ovu valutu podržalo je samo obećanje da će im vlada vratiti dugove. Ovo je poznato kao monetizacija duga.
Budući da su ratne obveznice i valuta samo komadi papira, one su lake i jeftine za proizvodnju i mogu se napraviti u ogromnim količinama. Ono što ograničava proizvodnju i jednog i drugog je poverenje.
Ima smisla da se neko rastane od svog teško stečenog novca da kupi državnu obveznicu, samo ako veruje da će vlada da vrati svoj dug, plus kamate. Centralna banka je “krajnji kupac”, što znači da će ona da kupi državne obveznice kada to niko drugi neće da uradi.
Zapamtite, centralnu banku gotovo da ništa ne košta da kupi državne obveznice, jer oni sami štampaju valutu da bi ih kupili.
Zamislite da pridjete najskupljem automobilu u autosalonu – koji košta 100.000 USD. Mislite da je automobil lep, ali taj novac biste radije potrošili na lepši stan – tako da ste spremni da platite samo 40.000 USD za taj auto.
Sada, hajde da zamislimo da imate štampač za novac i da vas košta samo 50 USD za mastilo i papir da bi ištampali 1.000.000 USD. Vi biste odmah kupili auto, čak i ako biste morali da se cenkate sa drugim čovekom, i da ga na kraju platite 150.000 USD!
Ista stvar se dešava kada centralna banka kupuje obveznice (dugove) od vlade. Centralna banka može da stvori valutu toliko jeftino, da su spremni da plate i više nego što bi drugi platili ove obveznice i nastaviće da ih kupuju čak i kada niko drugi ne bude želeo.
Monetizacija duga uzrokuje inflaciju
Kada centralne banke monetizuju državni dug, funkcija novca kao zalihe vrednosti počinje da se nagriza. Vlada troši novi novac koji je dobila od svoje centralne banke na ratnu robu, obroke i još mnogo toga.
Cene roba rastu od ove novoštampane valute koja kruži kroz ekonomiju. Kada se cene povećavaju, to znači da se vrednost svake jedinice valute smanjuje. Svi koji drže valutu sada imaju manje vrednosti. Danas to nazivamo sporim gubitkom funkcije zalihe vrednosti u novčanoj inflaciji.
Za Nemačku nakon Prvog svetskog rata monetizacija duga izazvala je totalni slom Nemačke ekonomije i stvorila uslove za rast fašizma.
Kao deo sporazuma o prekidu vatre koji je okončao Prvi svetski rat, Nemačka je pobednicima morala da plati ogroman novac. Nemačkoj vladi je bio preko potreban novac, pa su prodale obveznice (dug) Rajhsbanci, nemačkoj centralnoj banci.
Ovaj postupak doveo je do toga da je vlada štampala toliko maraka (tadašnja nemačka valuta) da je tempo inflacije u Nemačkoj ubrzan u hiperinflaciju početkom 1920-ih. Cena vekne hleba za samo 4 godine popela se sa 1,2 marke na 428 biliona maraka.
Tokom i posle Prvog svetskog rata, SAD, Britanija, Francuska i mnoge druge vlade pratile su Nemačku u štampanju valute potpomognute državnim dugom.
To je dovelo do toga da su građani želeli da svoju papirnu valutu zamene za zlato, baš kao i penzioner iz priče o Kejnslandu.
Međutim, mnoge vlade su suspendovale konvertibilnost svojih valuta u zlato. Ovim potezom vlade su primorale svoje građane da drže nacionalnu papirnu valutu i gledaju kako se njihova ušteda smanjuje u vrednosti.
Da bi mogle da nastave da štampaju novac i da bi ga trošile na nepopularne programe za koje nisu mogle da skupljaju poreze za finansiranje – poput ratova.
Bretton Woods: Novi monetarni sistem
Nakon razaranja koja su donela dva svetska rata, vlade su uspostavile novi globalni monetarni sistem prema Bretton Woods-ovom sporazumu iz 1944. godine.
Prema ovom sporazumu, valuta svake države konvertovala se po fiksnom kursu sa američkim dolarom. Američki dolar je zauzvrat predstavljao zlato po stopi od 35 USD za jednu trojsku uncu zlata*.
Sve globalne valute su stoga još uvek bile jednostavna reprezentacija zlata, putem američkih dolara kao posrednika. Redovni građani više nisu mogli da otkupljuju svoje valute za zlato iz Sjedinjenih Država. Međutim, strane centralne banke mogle bi da dođu u Sjedinjene Države da bi zamenile dolare za zlato po stopi od 35 USD za jednu uncu zlata.
Međutim, vlada Sjedinjenih Država nije uvek držala dovoljno zlata da podrži sve dolare u opticaju. Američka vlada nastavila je da finansira proširene socijalne i vojne programe prodajom državnog duga svojoj centralnoj banci, Federalnim rezervama, koja je povećala ponudu dolara bez povećanja ponude zlata koja podupire te dolare.
*Trojna unca je standardna mera čistog zlata i ima malo veću težinu od normalne unce.
Propast Bretton Woods-a
Tokom 1970-ih, sve veći troškovi rata u Vijetnamu i stranih vlada koje su otkupljivale svoje dolare za zlato, stvorili su pritisak na Trezor Sjedinjenih Država.
Ponuda dolara je porasla, dok je zlato u posedu Sjedinjenih Država opalo. Od 1950. pa do početka 1970-ih, rezerve zlata koje je držala vlada Sjedinjenih Država smanjile su se za više od 50%, sa 20 metričkih tona na samo 8 metričkih tona.
Godine 1970. država je imala zlata u vrednosti od samo 12 biliona dolara po zvaničnom kursu od 35 dolara za trojsku uncu zlata. Tokom ovog istog vremenskog perioda, ukupna ponuda američkih dolara otišla je sa oko 32 biliona USD na skoro 70 biliona USD.
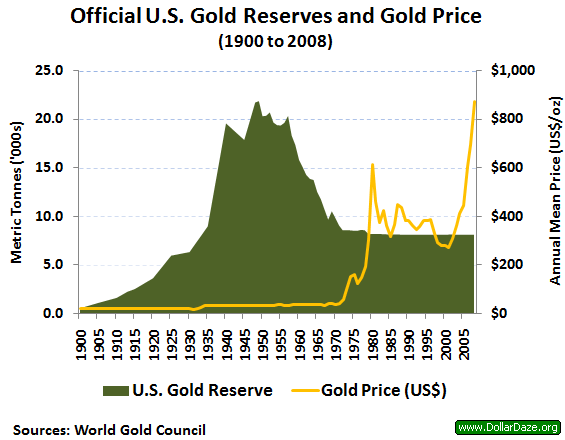 Zvanične rezerve zlata u SAD-u su naglo padale od 1950. do 1970. godine, dok su se dolari u opticaju povećavali. Izvor: Wikipedia, DollarDaze.org
Zvanične rezerve zlata u SAD-u su naglo padale od 1950. do 1970. godine, dok su se dolari u opticaju povećavali. Izvor: Wikipedia, DollarDaze.orgAmerička vlada nije bila u stanju da potkrepi dolare zlatom od 35 dolara po trojnoj unci, što dovelo do rizika za čitav globalni monetarni sistem.
Početkom sedamdesetih godina, trojna unca zlata trebala je da vredi 200 USD da bi u potpunosti podržala sve američke dolare u opticaju. Rečeno na drugi način, Sjedinjene Države su pokušavale da kažu svetu da jedan dolar vredi 1/35 trojne unce zlata, ali u stvarnosti dolar je vredeo samo 1/200 trojne unce.
Kad su strane vlade trebale da pribave dolare za međunarodnu trgovinu i rezerve, bile su opelješene. Francuska vlada je to shvatila šezdesetih godina prošlog veka i počela je da prodaje svoje američke dolare za zlato po zvaničnom kursu od 35 dolara za trojsku uncu zlata.
Zemlje su počinjale da se bude iz šeme američke vlade. SAD su krale bogatstvo putem emisione dobiti, prodajući dolare za 1/35 trojne unce zlata, kada su vredeli samo 1/200 trojske unce.
Nixonov Šok ulazi u ’tradicionalni’ novac
Da bi kuća od karata mogla da ostane na mestu, predsednik Nixon je 1971. najavio da će američka vlada privremeno da obustavi konvertibilnost dolara u zlato.
Strane vlade više nisu mogle da polažu pravo na zlato svojim papirnim dolarima, a dolar više nije bio “poduprt” zlatom. Nixon je tvrdio da će ovo stabilizovati dolar.
50 godina kasnije, kristalno je jasno da je ovo samo pomoglo dolaru da izgubi vrednost i da ovaj “privremeni” program još uvek traje.
Pre 1971. godine, sve globalne valute bile su vezane za američki dolar putem Bretton Woods-ovog sporazuma. Kada je Nixon promenio američki dolar iz dolara podržanog u zlatu u dolar podržan dugom, ovim je promenio i svaku drugu valutu na Zemlji.
Sam je učinio da se celokupna svetska ekonomija zasniva na dugovima. Valute više nisu predstavljale zlato, već su predstavljale vrednost državnog duga.
Zlatni Standard se nikada nije vratio
Konvertibilnost američkih dolara u zlato – zlatni standard – nikada se nije vratio.
Od 1971. godine, čitav globalni monetarni sistem pokreće se tradicionalnim “fiat” valutama: poverenjem u vladine institucije da održavaju valutni sistem.
Većina valuta podržana je kombinacijom duga njihove vlade i drugih tradicionalnih valuta poput dolara i evra. Papirne valute više nisu podržane zlatom, imovinom koja je više od 5000 godina služila kao težak novac.
Danas vas vlade prisiljavaju da plaćate porez u njihovoj valuti i manipulišu saznanjima oko novca kako bi osigurale da potražnja za njihovom valutom ostane velika.
To im omogućava da neprestano štampaju više valuta, da bi je potrošili na vladine projekte, uzrokujući inflaciju cena koja jede i smanjuje bogatstvo i plate.
Američka vlada sada prodaje državne obveznice (dugove), poznate kao obveznice Trezora SAD, eng. US Treasuries, komercijalnim bankama u zamenu za američke dolare.
Vlada koristi te dolare za finansiranje svog budžetskog deficita. Komercijalne banke prodaju mnoge obveznice Trezora SAD, koje su kupile, američkoj centralnoj banci, Federalnim Rezervama.
Federalne rezerve plaćaju komercijalnim bankama sveže štampanim novcem “pomoću računara i upisivanjem količine na račun”, kako je rekao bivši predsednik Fed-a Ben Bernanke.
Ove komercijalne banke često zarađuju samo kupujući obveznice Trezora SAD od države i prodajući ih centralnoj banci. Kupujte nisko, prodajte visoko.
Centralne banke ovaj proces kupovine državnog duga – odnosno pozajmljivanja novca državi – nazivaju operacijama otvorenog tržišta.
Kada centralna banka odjednom kupi velike iznose duga, oni to nazivaju kvantitativnim ublažavanjem. Centralne banke javno najavljuju kupovinu državnog duga, ali vrlo malo ljudi razume šta to zapravo znači.
Euro, jen i svaka druga valuta koja se danas koristi funkcionišu slično kao američki dolar.
Da li će SAD ikada vratiti svoj nacionalni dug? Neobična stvar u vezi sa državnim dugom SAD-a je ta što vlada poseduje štampariju potrebnu za njegovu otplatu.
Kao rezultat toga, kada vlada duguje novac, oni samo pozajme još više novca da bi otplatile taj dug, povećavajući nacionalni dug.
Ako vam ovo zvuči kao Ponzijeva piramidalna šema, to je zato što ona to i jeste – najveća Ponzijeva šema u istoriji. Kao i svaka Ponzijeva šema, nastaviće se sve dok su ljudi koji kupuju Ponzijevu šemu budu uvereni da će im biti plaćeno nazad.
Ako ljudi i nacije prestanu da se zadužuju i koriste američke dolare jer nemaju poverenja u američku vladu ili vide da cena robe raste (tj. dolar postaje sve manje vredan), potražnja za dolarom će opadati, što će izazvati začaranu spiralu.
Ova spirala često završi u hiperinflaciji, kao što smo videli u novijoj istoriji sa Jugoslavijom, Venecuelom, Argentinom, Zimbabveom i mnogim drugim državama.
Ovo je način kako funkcioniše novac na vašem bankovnom računu. Novac svake nacije na svetu pati od istih problema kao i perle i novčanice u pričama o Njutoniji i Kejnslandu.
Kako banke i vlade kradu tvoj novac?
Tokom vekova, stigli smo do monetarnog sistema u kojem banke i vlade mogu da štampaju novu valutu za finansiranje svojih operacija i svojih prijatelja u zločinu, dok kradu bogatstvo svojih građana.
Šta će se desiti sa svetom kada novac bude mogao da štampa svaki narod na planeti?
- Bogatstvo onih koji su blizu pravljenja nove valute se povećava
- Vlada i politički povlašćena klasa ljudi, imaju pristup novoštampanom novcu pre svih ostalih, pa mogu da ga potroše pre nego što cene porastu. Na ovaj efekat pokazao je ekonomista Richard Cantillon sredinom 1700-ih i poznat je kao Cantillonov Efekat.
- Cena robe raste (poznato kao inflacija)
- Ne raste sve roba istovremeno u ceni. Roba blizu mesta gde se proizvodi nova valuta – finansijski sektor i vlada – prva raste, i odatle uzrokuje efekt talasa na cene.
- Inflacija se često predstavlja kao promena cene potrošačke korpe, poznata kao Indeks Potrošačkih Cena, eng. Consumer Price Index (CPI). Vlada ima alate za manipulisanje ovim brojem kako bi osigurala da se ona čini niskom i stabilnom, kao što je objašnjeno u našem članku o inflaciji.
- Finansijska imovina često primećuje ogromnu inflaciju, ali bankari to ne nazivaju inflacijom – oni kažu da naša ekonomija cveta! Nakon što su američke Federalne rezerve učetvorostručile ponudu američkih dolara u šest godina nakon finansijske krize 2008. godine, banke koje su dobile te nove dolare, kupile su akcije i obveznice, stvarajući ogroman balon u cenama ove imovine.
- Štednja i životni standard stanovništva se smanjuju
- Plate su jedna od poslednjih “cena” u ekonomiji koja se prilagođava, jer se često povećavaju samo jednom godišnje. U međuvremenu, cene dnevnih potrepština te osobe koja zaradjuje platu neprestano rastu kako novi novac kruži ekonomijom.
- Najviše su pogođeni oni koji žive od plate do plate – a to je 70% Amerikanaca.
- Razlike u prihodima između bogatih i siromašnih se povećavaju, kao što se vidi na grafikonu ispod.
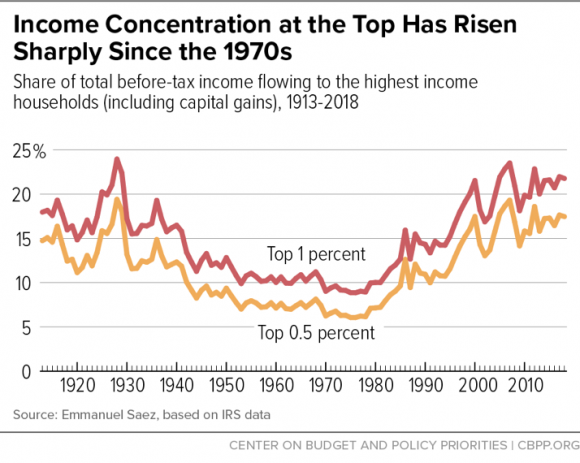 Koncentracija Dohotka na Vrhu Naglo je Porasla od 1970-ih
(Udeo u ukupnom prihodu pre oporezivanja u domaćinstvima sa najvišim dohotkom (uključujući kapitalne dobitke), 1913-2018)
Koncentracija Dohotka na Vrhu Naglo je Porasla od 1970-ih
(Udeo u ukupnom prihodu pre oporezivanja u domaćinstvima sa najvišim dohotkom (uključujući kapitalne dobitke), 1913-2018)Zašto i dalje imamo isti monetarni sistem?
Ako ovaj sistem bogate još više obogaćuje, a siromašne još više osiromašuje, dovodeći do političke nestabilnosti, zašto ga onda ne bismo promenili?
Najveći razlog zašto se ništa ne menja je verovatno to što puno toga ne znamo o samom sistemu. Svi svakodnevno koristimo valute svojih vlada, ali većina nas ne razume kako sistem funkcioniše i šta on čini našim društvima.
Obrazovni sistem, mediji i finansijski stručnjaci neprestano nam govore da je monetarni sistem previše komplikovan da bi ga normalni ljudi razumeli. Mnogi od nas se zato i ne trude da pokušaju.
Još nekoliko razloga zašto ovaj sistem nastavlja da opstaje:
- Mnogo je ljudi koji imaju direktnu korist od štampanja novog novca.
- Ti ljudi ne žele nikakve promene i bore se da zadrže tu moć.
- Nacionalne valute su često pogodne
- Kreditne kartice, online bankarstvo i još mnogo toga čine upravljanje nacionalnim valutama i njihovo trošenje lakim i jednostavnim.
- Građani moraju da plaćaju porez u svojoj nacionalnoj valuti
- To stvara potražnju za tom valutom od svih građana, povećavajući njenu vrednost.
- Glavna međunarodna tržišta, poput nafte, denominirana su u dolarima.
- Nafta je potrebna svakoj zemlji na planeti, ali pošto mnogi ne mogu da je proizvode, moraju da je kupuju na međunarodnim berzama. Od 1970-ih na ovim berzama gotovo sva nafta se prodaje za dolare, što stvara potražnju za dolarima. Da bi se odmaknule od ovog sistema, zemlje bi trebale da pronađu novu valutu ili robu za trgovinu naftom, što zahteva vreme i rizike.
- Nije postojala dobra alternativa
- Uz globalnu ekonomiju u realnom vremenu, naš sistem digitalnog bankarstva koji koristi nacionalne valute je pogodan. Transakcija u tvrdom novcu poput zlata bila bi previše nezgrapna za današnji svet. Digitalna valuta pod nazivom Bitcoin, predstavljena 2009. godine, je rastuća alternativa koja nudi čvrst novac koji se kreće brzinom interneta.
Šta je novac, i zašto trebate da brinete?
Novac je alat koji olakšava razmenu dobara. Kao i svako drugo dobro, novac se pridržava zakona ponude i potražnje – povećanje potražnje povećaće njegovu vrednost, a povećanje ponude smanjiće njegovu vrednost.
Na ovaj način novac se ne razlikuje od kuće ili piletine. Međutim, velika prodajnost novca znači da je potražnja za njim uvek velika. Kao rezultat, novac mora biti težak za proizvodnju (a samim tim i ograničen u ponudi) ili će ga onaj ko ga može napraviti, stvoriti toliko, da vremenom više neće služiti kao zaliha vrednosti. Uskoro će izgubiti svoje funkcije kao sredstvo razmene i obračunske jedinice.
Najbolji novac u datoj ekonomiji je onaj koji se najslobodnije kreće – svi ga žele, lako je obaviti transakcije sa njim i koji sa vremenom dobro drži svoju vrednost. Nijedan novac nije savršen u svemu ovome, a neki ističu jednu funkciju novca na štetu drugih.
Iako se istorija ne ponavlja, ona se rimuje, a usponi i padovi monetarnih sistema imaju jasne ritmove. Uspon i pad monetarnog sistema često sledi opšti obrazac koji smo videli u pričama o agri perlama i Kejnslandu: pojavljuje se odredjenji oblik novca koji pomaže ljudima da efikasnije trguju i štede, ali na kraju gubi na vrednosti kada neko shvati kako da ga jeftino stvori u velikoj količini. Međutim, tokom dugog perioda vremena, monetarni sistemi su se poboljšali u sve tri funkcije novca.
Na primer, zlato je tokom vremena dobro služilo kao zaliha vrednosti. Međutim, naša međusobno povezana ekonomija ne bi mogla efikasno da funkcioniše ako bi trebalo da fizičko zlato zamenimo robom i uslugama. Mnogo je lakše kretati se na papirnom i digitalnom novcu, ali istorija nam govori da su vlade i bankari iskoristili ove oblike novca za krađu bogatstva putem inflacije.
Današnji globalni monetarni sistem je vrlo zgodan, a digitalna plaćanja i kreditne kartice olakšavaju trošenje novca. Ovo skriva stalnu inflaciju koja nagriza vrednost svake jedinice novca i dovodi do sve većeg jaza u bogatstvu.
Nadam se da je ovaj članak proširio vaše razumevanje novca i njegove uloge u društvu. Ovo je samo početak svega što treba istražiti o novcu: za kasnije su sačuvane teme o inflaciji, kamatnim stopama, pozajmljivanju, poslovnim ciklusima i još mnogo toga.
Efikasnija Ušteda Novca
Možda se pitate kako zaštititi svoju štednju kada svaki oblik često korišćenog novca i investicija pati od inflacije ponude – koja umanjuje vrednost i prenosi bogatstvo onima koji mogu da stvore novac ili investiciju. Možda se čini da se ništa na planeti danas ne može kvalifikovati kao ‘težak’ novac, ali dve stvari ipak ostaju: zlato i njegov noviji rođak Bitcoin. Obe ove stvari je neverovatno teško proizvesti, a jedna od njih se kreće brzinom interneta i može se čuvati u vašem mozgu.
Ako želite da saznate više o Bitcoin-u kao sredstvu za zaštitu vaše ušteđevine, pročitajte ovde. Ako ste već spremni za kupovinu Bitcoin-a, pogledajte moj vodič za kupovinu Bitcoin-a. Možete početi sa investiranjem sa samo 5 ili 10 €.

Zasluge
Hvala svima koji su pomogli u izradi i uređivanju ove serije o novcu: @ck_SNARKS, @CryptoRothbard, Neil Woodfine, Emil Sandstedt, Taylor Pearson, Parker Lewis, Jason Choi, mojoj porodici i mnogim drugima.
Hvala svima koji su ovo inspirisali i razvili ključne ideje koje su ovde primenjene: Friedrich Hayek, Carl Menger, Ludwig Von Mises, Murray Rothbard, Saifedean Ammous, Dan Held, Pierre Rochard, Stephan Livera, Michael Goldstein, i mnogi drugi.
Molim vas da šerujete! Ako vam je ovaj članak otvorio oči o tome kako funkcioniše naš novac i finansijski sistem, kontaktirajte me ili ostavite komentar!
Ako vam se sviđa moj rad, molim vas da ga podelite sa svojim prijateljima i porodicom. Cilj mi je da svima pružim pogled u ekonomiju i na to kako ona utiče na njihov život.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:46:11
@ 6d5c826a:4b27b659
2025-05-23 21:46:11- GLPI - Information Resource-Manager with an additional Administration Interface. (Source Code)
GPL-3.0PHP - OCS Inventory NG - Asset management and deployment solution for all devices in your IT Department. (Source Code)
GPL-2.0PHP/Perl - OPSI - Hardware and software inventory, client management, deployment, and patching for Linux and Windows. (Source Code)
GPL-3.0/AGPL-3.0OVF/Python - RackTables - Datacenter and server room asset management like document hardware assets, network addresses, space in racks, networks configuration. (Demo, Source Code)
GPL-2.0PHP - Ralph - Asset management, DCIM and CMDB system for large Data Centers as well as smaller LAN networks. (Demo, Source Code)
Apache-2.0Python/Docker - Snipe IT - Asset & license management software. (Source Code)
AGPL-3.0PHP
- GLPI - Information Resource-Manager with an additional Administration Interface. (Source Code)
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-23 19:32:28
@ 5d4b6c8d:8a1c1ee3
2025-05-23 19:32:28https://primal.net/e/nevent1qvzqqqqqqypzp6dtxy5uz5yu5vzxdtcv7du9qm9574u5kqcqha58efshkkwz6zmdqqszj207pl0eqkgld9vxknxamged64ch2x2zwhszupkut5v46vafuhg9833px
Some of my colleagues were talking about how they're even more scared of RFK Jr. than they are of Trump. I hope he earns it.
https://stacker.news/items/987685
-
 @ 6d5c826a:4b27b659
2025-05-23 21:45:53
@ 6d5c826a:4b27b659
2025-05-23 21:45:53- BounCA - A personal SSL Key / Certificate Authority web-based tool for creating self-signed certificates. (Source Code)
Apache-2.0Python - easy-rsa - Bash script to build and manage a PKI CA.
GPL-2.0Shell - Fusion Directory - Improve the Management of the services and the company directory based on OpenLDAP. (Source Code)
GPL-2.0PHP - LDAP Account Manager (LAM) - Web frontend for managing entries (e.g. users, groups, DHCP settings) stored in an LDAP directory. (Source Code)
GPL-3.0PHP - Libravatar - Libravatar is a service which delivers your avatar (profile picture) to other websites. (Source Code)
AGPL-3.0Python - Pomerium - An identity and context aware access-proxy inspired by BeyondCorp. (Source Code)
Apache-2.0Docker/Go - Samba - Active Directory and CIFS protocol implementation. (Source Code)
GPL-3.0C - Smallstep Certificates - A private certificate authority (X.509 & SSH) and related tools for secure automated certificate management. (Source Code)
Apache-2.0Go - ZITADEL - Cloud-native Identity & Access Management solution providing a platform for secure authentication, authorization and identity management. (Source Code)
Apache-2.0Go/Docker/K8S
- BounCA - A personal SSL Key / Certificate Authority web-based tool for creating self-signed certificates. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:45:34
@ 6d5c826a:4b27b659
2025-05-23 21:45:34- Authelia - The Single Sign-On Multi-Factor portal for web apps. (Source Code)
Apache-2.0Go - Authentik - Flexible identity provider with support for different protocols. (OAuth 2.0, SAML, LDAP and Radius). (Source Code)
MITPython - KeyCloak - Open Source Identity and Access Management. (Source Code)
Apache-2.0Java
- Authelia - The Single Sign-On Multi-Factor portal for web apps. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:45:15
@ 6d5c826a:4b27b659
2025-05-23 21:45:15- 389 Directory Server - Enterprise-class Open Source LDAP server for Linux. (Source Code)
GPL-3.0C - Apache Directory Server - Extensible and embeddable directory server, certified LDAPv3 compatible, with Kerberos 5 and Change Password Protocol support, triggers, stored procedures, queues and views. (Source Code)
Apache-2.0Java - FreeIPA - Integrated security information management solution combining Linux (Fedora), 389 Directory Server, Kerberos, NTP, DNS, and Dogtag Certificate System (web interface and command-line administration tools). (Source Code)
GPL-3.0Python/C/JavaScript - FreeRADIUS - Multi-protocol policy server (radiusd) that implements RADIUS, DHCP, BFD, and ARP and associated client/PAM library/Apache module. (Source Code)
GPL-2.0C - lldap - Light (simplified) LDAP implementation with a simple, intuitive web interface and GraphQL support.
GPL-3.0Rust - OpenLDAP - Open-source implementation of the Lightweight Directory Access Protocol (server, libraries and clients). (Source Code)
OLDAP-2.8C
- 389 Directory Server - Enterprise-class Open Source LDAP server for Linux. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:44:57
@ 6d5c826a:4b27b659
2025-05-23 21:44:57- Atom Community - A fork of atom A hackable text editor from Github.
MITJavaScript - Brackets - Code editor for web designers and front-end developers. (Source Code)
MITJavaScript - Eclipse - IDE written in Java with an extensible plug-in system. (Source Code)
EPL-1.0Java - Geany - GTK2 text editor. (Source Code)
GPL-2.0C/C++ - GNU Emacs - An extensible, customizable text editor-and more. (Source Code)
GPL-3.0C - Haroopad - Markdown editor with live preview. (Source Code)
GPL-3.0JavaScript - jotgit - Git-backed real-time collaborative code editing.
MITNodejs - KDevelop - IDE by the people behind KDE. (Source Code)
GFDL-1.2C++ - Micro - A modern and intuitive terminal-based text editor. (Source Code)
MITGo - Nano - Easy to use, customizable text editor. (Source Code)
GPL-3.0C - Notepad++ - GPLv2 multi-language editor with syntax highlighting for Windows. (Source Code)
GPL-2.0C++ - TextMate - A graphical text editor for OS X. (Source Code)
GPL-3.0C++ - Vim - A highly configurable text editor built to enable efficient editing. (Source Code)
VimC - VSCodium - An open source cross-platform extensible code editor based on VS Code by Microsoft removing their non-free additions. (Source Code)
MITTypeScript
- Atom Community - A fork of atom A hackable text editor from Github.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:44:34
@ 6d5c826a:4b27b659
2025-05-23 21:44:34- Bind - Versatile, classic, complete name server software. (Source Code)
MPL-2.0C - CoreDNS - Flexible DNS server. (Source Code)
Apache-2.0Go - djbdns - A collection of DNS applications, including tinydns. (Source Code)
CC0-1.0C - dnsmasq - Provides network infrastructure for small networks: DNS, DHCP, router advertisement and network boot. (Source Code)
GPL-2.0C - Knot - High performance authoritative-only DNS server. (Source Code)
GPL-3.0C - NSD - Authoritative DNS name server developed speed, reliability, stability and security. (Source Code)
BSD-3-ClauseC - PowerDNS Authoritative Server - Versatile nameserver which supports a large number of backends. (Source Code)
GPL-2.0C++ - Unbound - Validating, recursive, and caching DNS resolver. (Source Code)
BSD-3-ClauseC - Yadifa - Clean, small, light and RFC-compliant name server implementation developed from scratch by .eu. (Source Code)
BSD-3-ClauseC
- Bind - Versatile, classic, complete name server software. (Source Code)
-
 @ 3c389c8f:7a2eff7f
2025-05-23 18:23:28
@ 3c389c8f:7a2eff7f
2025-05-23 18:23:28I've sporadically been trying to spend some time familiarizing myself with Nostr marketplace listings and the clients that support them. I have been pleased with what I have encountered. The clients are simple to use, and people have been receptive to transacting with me. I've sold items to both people whom I consider to be close contacts, as well as to people that I barely know.
My first attempt was close to 2 years ago, when I listed one pound bags of coffee for sale. If I remember correctly, there was only one marketplace client then, and it only had support for extension signing. At the time, my old laptop had just died so I couldn't really interact with my listings through that client. (I have never had much luck with extensions on mobile browsers, so I have never attempted to use one for Nostr.) Instead, I used Amethyst to list my product and exchange messages with potential buyers. The Amethyst approach to handling different Nostr events is brilliant to me. You can do some part of each thing but not all. I view it as great introduction to what Nostr is capable of doing and a gateway to discovering other clients. Marketplace listings on Amethyst are handled in that fashion. You can list products for sale. You can browse and inquire about products listed by your contacts or by a more "global" view, which in the case of Nostr, would be products listed by anyone who publishes their listings to any of the relays that I connect with to read. There is no delete option, should a product sell out, and there is no direct purchase option. All sales need to be negotiated through direct messages. Though it has limited functionality, the system works great for items that will be listed for repeated sale, such as my coffee. If one were to list a one-off item and sell it, the flow to delete the listing would be easy enough. Copy the event ID, visit delete.nostr.com , and remove the product. Should there be a price change, it would be necessary to visit a full marketplace client to edit the listing, though one could easily delete and start over as well. Anyway, much to my surprise I sold more coffee than I had anticipated through that listing. People were eager to try out the feature and support a small business. This was an awesome experience and I see no reason to avoid buying or selling products on Nostr, even if the only client available to you is Amethyst. (Which I think might be the only mobile app with marketplace support.) It is completely manageable.
Later, I tried to list a pair of nearly new shoes. Those did not sell. I have a sneaking suspicion that there were very few people that wore size USw6 shoes using Nostr at the time. Even though no one wanted my shoes, I still ended up having some interesting conversations about different styles of running shoes, boots, and other footwear talk. I can't call the listing a total bust, even though I ended up deleting the listing and donating those shoes to the YWCA. After some number of months watching and reading about development in the Nostr marketplace space, I decided to try again.
This second approach, I started with niche rubber duckies that, for reasons unbeknownst to most, I just happen to have an abundance of. It occurred to me that day that I would most likely be creating most of my listings via mobile app since that is also my main method of taking pictures these days. I could sync or send them, but realistically it's just adding extra steps for me. I listed my ducks with Amethyst (all of which are currently still available, surprise, surprise.). I immediately went to check how the listing renders in the marketplace clients. There are 2 where I can view it, and the listing looks nice, clean, organized in both places. That alone is reason enough to get excited about selling on Nostr. Gone are the days of "this item is cross-posted to blah, blah, blah" lest risk being kicked out of the seller groups on silo'd platforms.
Knowing I can't take it personally that literally no one else on Nostr has an affinity for obscure rubber ducks (that they are willing to admit), I leave my duckies listed and move on. My next listing is for artisan bracelets. Ones that I love to make. I made my mobile listing, checked it across clients and this time I noticed that shopstr.store is collecting my listings into a personal seller profile, like a little shop. I spent some time setting up the description and banner, and now it looks really nice. This is great, since the current site acts as an open and categorized market for all sellers. Maybe someone will see the bracelets while browsing the clothing category and stumble upon the rubber ducky of their dreams in the process. That hasn't happened yet, but I was pretty jazzed to sell a few bracelets right away. Most of the sale and exchange happened via DM, for which I switched to Flotilla because it just handles messaging solidly for me. I made some bracelets, waited a few weeks, then visited Shopstr again to adjust the price. That worked out super well. I noticed that a seller can also list in their preferred currency, which is very cool. Meanwhile, back to my social feed, I can see my listing posted again since there was an edit. While not always the best thing to happen with edits, it is great that it happens with marketplace listings. It removes all the steps of announcing a price reduction, which would be handy for any serious seller. I am very happy with the bracelet experience, and I will keep that listing active and reasonably up to date for as long as any interest arises. Since this has all gone so well, I've opted to continue listing saleable items to Nostr first for a few days to a few weeks prior to marketing them anywhere else.
Looking at my listings on cypher.space, I can see that this client is tailored more towards people who are very passionate about a particular set of things. I might not fall into this category but my listings still look very nice displayed with my writing, transposed poetry, and recipes. I could see this being a great space for truly devotional hobbyists or sellers who are both deeply knowledgeable about their craft and also actively selling. My experience with all 3 of these marketplace-integrated clients had been positive and I would say that if you are considering selling on Nostr, it is worth the effort.
As some sidenotes:
-
I am aware that Shopstr has been built to be self-hosted and anyone interested in selling for the long term should at least consider doing so. This will help reduce the chances of Nostr marketplaces centralizing into just another seller-silo.
-
Plebeian Market is out there, too. From the best I could tell, even though this is a Nostr client, those listings are a different kind than listings made from the other clients referenced here. I like the layout and responsiveness of the site but I opted not to try it out for now. Cross-posting has been the bane of online selling for me for quite some time. If they should migrate to an interoperable listing type (which I think I read may happen in the future), I will happily take that for a spin, too.
-
My only purchase over Nostr marketplaces so far was some vinyls, right around the time I had listed my coffee. It went well, the seller was great to work with, everything arrived in good shape. I have made some other purchases through Nostr contacts, but those were conversations that lead to non-Nostr seller sites. I check the marketplace often, though, for things I may want/need. The listings are changing and expanding rapidly, and I foresee more purchases becoming a part of my regular Nostr experience soon enough.
-
I thought about including screenshots for this, but I would much rather you go check these clients out for yourself.
-
-
 @ ecda4328:1278f072
2025-05-23 18:16:24
@ ecda4328:1278f072
2025-05-23 18:16:24And what does it mean to withdraw back to Bitcoin Layer 1?
Disclaimer: This post was written with help from ChatGPT-4o. If you spot any mistakes or have suggestions — feel free to reply or zap in feedback!
Let’s break it down — using three popular setups:
1. Wallet of Satoshi (WoS)
Custodial — you don’t touch Lightning directly
Sending sats:
- You open WoS, paste a Lightning invoice, hit send.
- WoS handles the payment entirely within their system.
- If recipient uses WoS: internal balance update.
- If external: routed via their node.
- You never open channels, construct routes, or sign anything.
Withdrawing to L1:
- You paste a Bitcoin address.
- WoS sends a regular on-chain transaction from their custodial wallet.
- You pay a fee. It’s like a bank withdrawal.
You don’t interact with Lightning directly. Think of it as a trusted 3rd party Lightning “bank”.
2. Phoenix Wallet
Non-custodial — you own keys, Phoenix handles channels
Sending sats:
- You scan a Lightning invoice and hit send.
- Phoenix uses its backend node (ACINQ) to route the payment.
- If needed, it opens a real 2-of-2 multisig channel on-chain automatically.
- You own your keys (12-word seed), Phoenix abstracts the technical parts.
Withdrawing to L1:
- You enter your Bitcoin address.
- Phoenix closes your Lightning channel (cooperatively, if possible).
- Your sats are sent as a real Bitcoin transaction to your address.
You’re using Lightning “for real,” with real Bitcoin channels — but Phoenix smooths out the UX.
3. Your Own Lightning Node
Self-hosted — you control everything
Sending sats:
- You manage your channels manually (or via automation).
- Your node:
- Reads the invoice
- Builds a route using HTLCs
- Sends the payment using conditional logic (preimages, time locks).
- If routing fails: retry or adjust liquidity.
Withdrawing to L1:
- You select and close a channel.
- A channel closing transaction is broadcast:
- Cooperative = fast and cheap
- Force-close = slower, more expensive, and time-locked
- Funds land in your on-chain wallet.
You have full sovereignty — but also full responsibility (liquidity, fees, backups, monitoring).
Core Tech Behind It: HTLCs, Multisig — and No Sidechain
- Lightning channels = 2-of-2 multisig Bitcoin addresses
- Payments = routed via HTLCs (Hashed Time-Locked Contracts)
- HTLCs are off-chain, but enforceable on-chain if needed
- Important:
- The Lightning Network is not a sidechain.
- It doesn't use its own token, consensus, or separate blockchain.
- Every Lightning channel is secured by real Bitcoin on L1.
Lightning = fast, private, off-chain Bitcoin — secured by Bitcoin itself.
Summary Table
| Wallet | Custody | Channel Handling | L1 Withdrawal | HTLC Visibility | User Effort | |--------------------|--------------|------------------------|---------------------|------------------|--------------| | Wallet of Satoshi | Custodial | None | Internal to external| Hidden | Easiest | | Phoenix Wallet | Non-custodial| Auto-managed real LN | Channel close | Abstracted | Low effort | | Own Node | You | Manual | Manual channel close| Full control | High effort |
Bonus: Withdrawing from LN to On-Chain
- WoS: sends sats from their wallet — like PayPal.
- Phoenix: closes a real channel and sends your UTXO on-chain.
- Own node: closes your multisig contract and broadcasts your pre-signed tx.
Bitcoin + Lightning = Sovereign money + Instant payments.
Choose the setup that fits your needs — and remember, you can always level up later.P.S. What happens in Lightning... usually stays in Lightning.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:44:16
@ 6d5c826a:4b27b659
2025-05-23 21:44:16- Atomia DNS - DNS management system.
ISCPerl - Designate - DNSaaS services for OpenStack. (Source Code)
Apache-2.0Python - DNSControl - Synchronize your DNS to multiple providers from a simple DSL. (Source Code)
MITGo/Docker - DomainMOD - Manage your domains and other internet assets in a central location. (Source Code)
GPL-3.0PHP - nsupdate.info - Dynamic DNS service. (Demo, Source Code)
BSD-3-ClausePython - octoDNS - DNS as code - Tools for managing DNS across multiple providers.
MITPython - Poweradmin - Web-based DNS control panel for PowerDNS server. (Source Code)
GPL-3.0PHP - SPF Toolbox - Application to look up DNS records such as SPF, MX, Whois, and more. (Source Code)
MITPHP
- Atomia DNS - DNS management system.
-
 @ 0e9491aa:ef2adadf
2025-05-24 07:01:14
@ 0e9491aa:ef2adadf
2025-05-24 07:01:14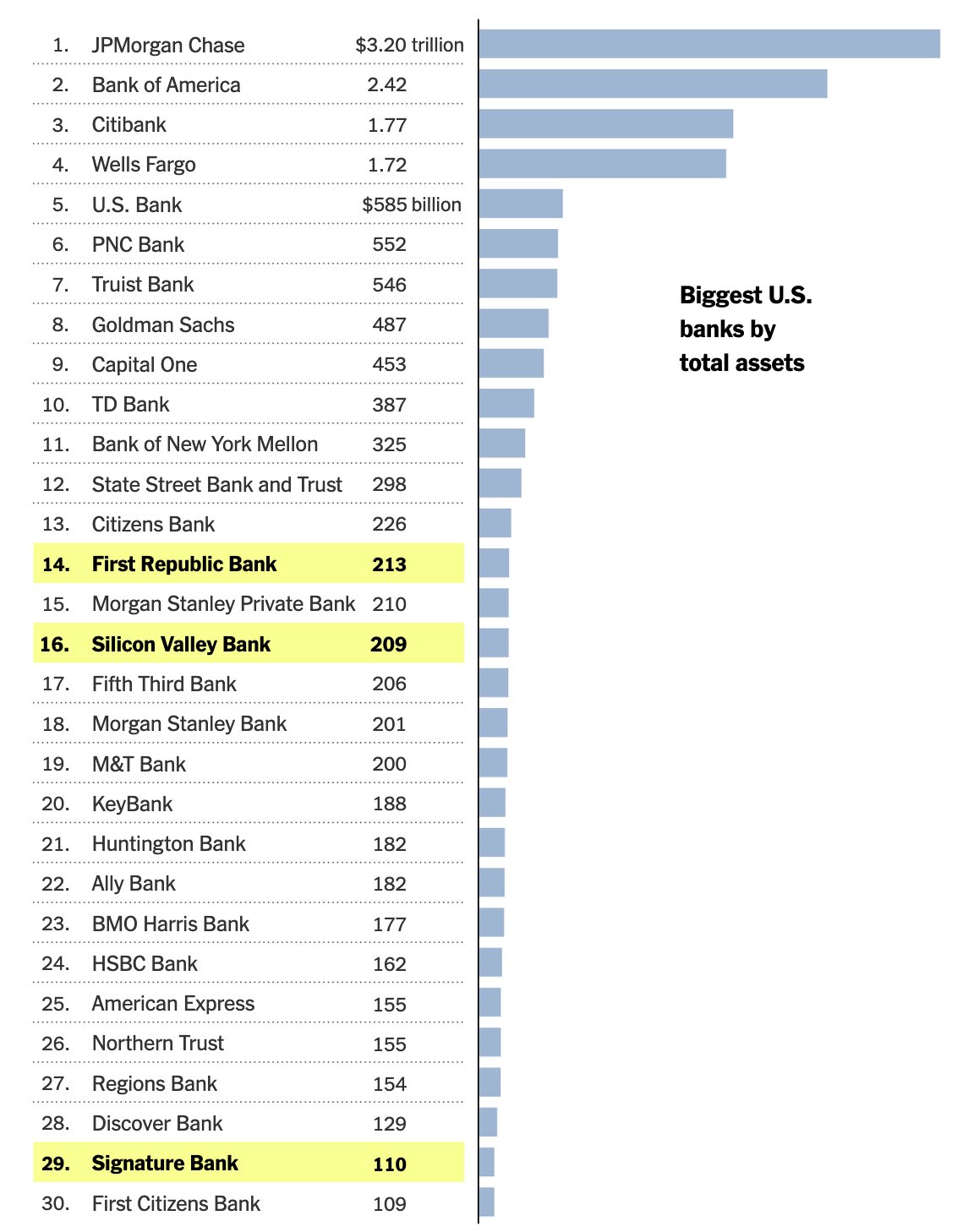
Bank run on every crypto bank then bank run on every "real" bank.
— ODELL (@ODELL) December 14, 2022
Good morning.
It looks like PacWest will fail today. It will be both the fifth largest bank failure in US history and the sixth major bank to fail this year. It will likely get purchased by one of the big four banks in a government orchestrated sale.
March 8th - Silvergate Bank
March 10th - Silicon Valley Bank
March 12th - Signature Bank
March 19th - Credit Suisse
May 1st - First Republic Bank
May 4th - PacWest Bank?PacWest is the first of many small regional banks that will go under this year. Most will get bought by the big four in gov orchestrated sales. This has been the playbook since 2008. Follow the incentives. Massive consolidation across the banking industry. PacWest gonna be a drop in the bucket compared to what comes next.
First, a hastened government led bank consolidation, then a public/private partnership with the remaining large banks to launch a surveilled and controlled digital currency network. We will be told it is more convenient. We will be told it is safer. We will be told it will prevent future bank runs. All of that is marketing bullshit. The goal is greater control of money. The ability to choose how we spend it and how we save it. If you control the money - you control the people that use it.
If you found this post helpful support my work with bitcoin.

-
 @ 866e0139:6a9334e5
2025-05-23 17:57:24
@ 866e0139:6a9334e5
2025-05-23 17:57:24Autor: Caitlin Johnstone. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Ich hörte einem jungen Autor zu, der eine Idee beschrieb, die ihn so sehr begeisterte, dass er die Nacht zuvor nicht schlafen konnte. Und ich erinnerte mich daran, wie ich mich früher – vor Gaza – über das Schreiben freuen konnte. Dieses Gefühl habe ich seit 2023 nicht mehr gespürt.
Ich beklage mich nicht und bemitleide mich auch nicht selbst, ich stelle einfach fest, wie unglaublich düster und finster die Welt in dieser schrecklichen Zeit geworden ist. Es wäre seltsam und ungesund, wenn ich in den letzten anderthalb Jahren Freude an meiner Arbeit gehabt hätte. Diese Dinge sollen sich nicht gut anfühlen. Nicht, wenn man wirklich hinschaut und ehrlich zu sich selbst ist in dem, was man sieht.
Es war die ganze Zeit über so hässlich und so verstörend. Es gibt eigentlich keinen Weg, all diesen Horror umzudeuten oder irgendwie erträglich zu machen. Alles, was man tun kann, ist, an sich selbst zu arbeiten, um genug inneren Raum zu schaffen, um die schlechten Gefühle zuzulassen und sie ganz durchzufühlen, bis sie sich ausgedrückt haben. Lass die Verzweiflung herein. Die Trauer. Die Wut. Den Schmerz. Lass sie deinen Körper vollständig durchfließen, ohne Widerstand, und steh dann auf und schreibe das nächste Stück.
Das ist es, was Schreiben für mich jetzt ist. Es ist nie etwas, worüber ich mich freue, es zu teilen, oder wofür ich von Inspiration erfüllt bin. Wenn überhaupt, dann fühlt es sich eher so an wie: „Okay, hier bitte, es tut mir schrecklich leid, dass ich euch das zeigen muss, Leute.“ Es ist das Starren in die Dunkelheit, in das Blut, in das Gemetzel, in die gequälten Gesichter – und das Aufschreiben dessen, was ich sehe, Tag für Tag.
Nichts daran ist angenehm oder befriedigend. Es ist einfach das, was man tut, wenn ein Genozid in Echtzeit vor den eigenen Augen stattfindet, mit der Unterstützung der eigenen Gesellschaft. Alles daran ist entsetzlich, und es gibt keinen Weg, das schönzureden – aber man tut, was getan werden muss. So, wie man es täte, wenn es die eigene Familie wäre, die da draußen im Schutt liegt.
Dieser Genozid hat mich für immer verändert. Er hat viele Menschen für immer verändert. Wir werden nie wieder dieselben sein. Die Welt wird nie wieder dieselbe sein. Ganz gleich, was passiert oder wie dieser Albtraum endet – die Dinge werden nie wieder so sein wie zuvor.
Und das sollten sie auch nicht. Der Holocaust von Gaza ist das Ergebnis der Welt, wie sie vor ihm war. Unsere Gesellschaft hat ihn hervorgebracht – und jetzt starrt er uns allen direkt ins Gesicht. Das sind wir. Das ist die Frucht des Baumes, den die westliche Zivilisation bis zu diesem Punkt gepflegt hat.
Jetzt geht es nur noch darum, alles zu tun, was wir können, um den Genozid zu beenden – und sicherzustellen, dass die Welt die richtigen Lehren daraus zieht. Das ist eines der würdigsten Anliegen, denen man sich in diesem Leben widmen kann.
Ich habe noch immer Hoffnung, dass wir eine gesunde Welt haben können. Ich habe noch immer Hoffnung, dass das Schreiben über das, was geschieht, eines Tages wieder Freude bereiten kann. Aber diese Dinge liegen auf der anderen Seite eines langen, schmerzhaften, konfrontierenden Weges, der in den kommenden Jahren vor uns liegt. Es gibt keinen Weg daran vorbei.
Die Welt kann keinen Frieden und kein Glück finden, solange wir uns nicht vollständig damit auseinandergesetzt haben, was wir Gaza angetan haben.
Dieser Text ist die deutsche Übersetzung dieses Substack-Artikels von Caitlin Johnstone.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 91bea5cd:1df4451c
2025-05-23 17:04:49
@ 91bea5cd:1df4451c
2025-05-23 17:04:49Em nota, a prefeitura justificou que essas alterações visam ampliar a segurança das praias, conforto e organização, para os frequentadores e trabalhadores dos locais. No entanto, Orla Rio, concessionária responsável pelos espaços, e o SindRio, sindicato de bares e restaurantes, ficou insatisfeita com as medidas e reforçou que a música ao vivo aumenta em mais de 10% o ticket médio dos estabelecimentos e contribui para manter os empregos, especialmente na baixa temporada.
De acordo com Paes, as medidas visam impedir práticas ilegais para que a orla carioca continue sendo um espaço ativo econômico da cidade: “Certas práticas são inaceitáveis, especialmente por quem tem autorização municipal. Vamos ser mais restritivos e duros. A orla é de todos”.
Saiba quais serão as 16 proibições nas praias do Rio de Janeiro
- Utilização de caixas de som, instrumentos musicais, grupos ou qualquer equipamento sonoro, em qualquer horário. Apenas eventos autorizados terão permissão.
- Venda ou distribuição de bebidas em garrafas de vidro em qualquer ponto da areia ou do calçadão.
- Estruturas comerciais ambulantes sem autorização, como carrocinhas, trailers, food trucks e barracas.
- Comércio ambulante sem permissão, incluindo alimentos em palitos, churrasqueiras, isopores ou bandejas térmicas improvisadas.
- Circulação de ciclomotores e patinetes motorizados no calçadão.
- Escolinhas de esportes ou recreações não autorizadas pelo poder público municipal.
- Ocupação de área pública com estruturas fixas ou móveis de grandes proporções sem autorização.
- Instalação de acampamentos improvisados em qualquer trecho da orla.
- Práticas de comércio abusivo ou enganosas, incluindo abordagens insistentes. Quiosques e barracas devem exibir cardápio, preços e taxas de forma clara.
- Uso de animais para entretenimento, transporte ou comércio.
- Hasteamento ou exibição de bandeiras em mastros ou suportes.
- Fixação de objetos ou amarras em árvores ou vegetação.
- Cercadinhos feitos por ambulantes ou quiosques, que impeçam a livre circulação de pessoas.
- Permanência de carrinhos de transporte de mercadorias ou equipamentos fora dos momentos de carga e descarga.
- Armazenamento de produtos, barracas ou equipamentos enterrados na areia ou depositados na vegetação de restinga.
- Uso de nomes, marcas, logotipos ou slogans em barracas. Apenas a numeração sequencial da prefeitura será permitida.
-
 @ c1e9ab3a:9cb56b43
2025-05-06 14:05:40
@ c1e9ab3a:9cb56b43
2025-05-06 14:05:40If you're an engineer stepping into the Bitcoin space from the broader crypto ecosystem, you're probably carrying a mental model shaped by speed, flexibility, and rapid innovation. That makes sense—most blockchain platforms pride themselves on throughput, programmability, and dev agility.
But Bitcoin operates from a different set of first principles. It’s not competing to be the fastest network or the most expressive smart contract platform. It’s aiming to be the most credible, neutral, and globally accessible value layer in human history.
Here’s why that matters—and why Bitcoin is not just an alternative crypto asset, but a structural necessity in the global financial system.
1. Bitcoin Fixes the Triffin Dilemma—Not With Policy, But Protocol
The Triffin Dilemma shows us that any country issuing the global reserve currency must run persistent deficits to supply that currency to the world. That’s not a flaw of bad leadership—it’s an inherent contradiction. The U.S. must debase its own monetary integrity to meet global dollar demand. That’s a self-terminating system.
Bitcoin sidesteps this entirely by being:
- Non-sovereign – no single nation owns it
- Hard-capped – no central authority can inflate it
- Verifiable and neutral – anyone with a full node can enforce the rules
In other words, Bitcoin turns global liquidity into an engineering problem, not a political one. No other system, fiat or crypto, has achieved that.
2. Bitcoin’s “Ossification” Is Intentional—and It's a Feature
From the outside, Bitcoin development may look sluggish. Features are slow to roll out. Code changes are conservative. Consensus rules are treated as sacred.
That’s the point.
When you’re building the global monetary base layer, stability is not a weakness. It’s a prerequisite. Every other financial instrument, app, or protocol that builds on Bitcoin depends on one thing: assurance that the base layer won’t change underneath them without extreme scrutiny.
So-called “ossification” is just another term for predictability and integrity. And when the market does demand change (SegWit, Taproot), Bitcoin’s soft-fork governance process has proven capable of deploying it safely—without coercive central control.
3. Layered Architecture: Throughput Is Not a Base Layer Concern
You don’t scale settlement at the base layer. You build layered systems. Just as TCP/IP doesn't need to carry YouTube traffic directly, Bitcoin doesn’t need to process every microtransaction.
Instead, it anchors:
- Lightning (fast payments)
- Fedimint (community custody)
- Ark (privacy + UTXO compression)
- Statechains, sidechains, and covenants (coming evolution)
All of these inherit Bitcoin’s security and scarcity, while handling volume off-chain, in ways that maintain auditability and self-custody.
4. Universal Assayability Requires Minimalism at the Base Layer
A core design constraint of Bitcoin is that any participant, anywhere in the world, must be able to independently verify the validity of every transaction and block—past and present—without needing permission or relying on third parties.
This property is called assayability—the ability to “test” or verify the authenticity and integrity of received bitcoin, much like verifying the weight and purity of a gold coin.
To preserve this:
- The base layer must remain resource-light, so running a full node stays accessible on commodity hardware.
- Block sizes must remain small enough to prevent centralization of verification.
- Historical data must remain consistent and tamper-evident, enabling proof chains across time and jurisdiction.
Any base layer that scales by increasing throughput or complexity undermines this fundamental guarantee, making the network more dependent on trust and surveillance infrastructure.
Bitcoin prioritizes global verifiability over throughput—because trustless money requires that every user can check the money they receive.
5. Governance: Not Captured, Just Resistant to Coercion
The current controversy around
OP_RETURNand proposals to limit inscriptions is instructive. Some prominent devs have advocated for changes to block content filtering. Others see it as overreach.Here's what matters:
- No single dev, or team, can force changes into the network. Period.
- Bitcoin Core is not “the source of truth.” It’s one implementation. If it deviates from market consensus, it gets forked, sidelined, or replaced.
- The economic majority—miners, users, businesses—enforce Bitcoin’s rules, not GitHub maintainers.
In fact, recent community resistance to perceived Core overreach only reinforces Bitcoin’s resilience. Engineers who posture with narcissistic certainty, dismiss dissent, or attempt to capture influence are routinely neutralized by the market’s refusal to upgrade or adopt forks that undermine neutrality or openness.
This is governance via credible neutrality and negative feedback loops. Power doesn’t accumulate in one place. It’s constantly checked by the network’s distributed incentives.
6. Bitcoin Is Still in Its Infancy—And That’s a Good Thing
You’re not too late. The ecosystem around Bitcoin—especially L2 protocols, privacy tools, custody innovation, and zero-knowledge integrations—is just beginning.
If you're an engineer looking for:
- Systems with global scale constraints
- Architectures that optimize for integrity, not speed
- Consensus mechanisms that resist coercion
- A base layer with predictable monetary policy
Then Bitcoin is where serious systems engineers go when they’ve outgrown crypto theater.
Take-away
Under realistic, market-aware assumptions—where:
- Bitcoin’s ossification is seen as a stability feature, not inertia,
- Market forces can and do demand and implement change via tested, non-coercive mechanisms,
- Proof-of-work is recognized as the only consensus mechanism resistant to fiat capture,
- Wealth concentration is understood as a temporary distribution effect during early monetization,
- Low base layer throughput is a deliberate design constraint to preserve verifiability and neutrality,
- And innovation is layered by design, with the base chain providing integrity, not complexity...
Then Bitcoin is not a fragile or inflexible system—it is a deliberately minimal, modular, and resilient protocol.
Its governance is not leaderless chaos; it's a negative-feedback structure that minimizes the power of individuals or institutions to coerce change. The very fact that proposals—like controversial OP_RETURN restrictions—can be resisted, forked around, or ignored by the market without breaking the system is proof of decentralized control, not dysfunction.
Bitcoin is an adversarially robust monetary foundation. Its value lies not in how fast it changes, but in how reliably it doesn't—unless change is forced by real, bottom-up demand and implemented through consensus-tested soft forks.
In this framing, Bitcoin isn't a slower crypto. It's the engineering benchmark for systems that must endure, not entertain.
Final Word
Bitcoin isn’t moving slowly because it’s dying. It’s moving carefully because it’s winning. It’s not an app platform or a sandbox. It’s a protocol layer for the future of money.
If you're here because you want to help build that future, you’re in the right place.
nostr:nevent1qqswr7sla434duatjp4m89grvs3zanxug05pzj04asxmv4rngvyv04sppemhxue69uhkummn9ekx7mp0qgs9tc6ruevfqu7nzt72kvq8te95dqfkndj5t8hlx6n79lj03q9v6xcrqsqqqqqp0n8wc2
nostr:nevent1qqsd5hfkqgskpjjq5zlfyyv9nmmela5q67tgu9640v7r8t828u73rdqpr4mhxue69uhkymmnw3ezucnfw33k76tww3ux76m09e3k7mf0qgsvr6dt8ft292mv5jlt7382vje0mfq2ccc3azrt4p45v5sknj6kkscrqsqqqqqp02vjk5
nostr:nevent1qqstrszamvffh72wr20euhrwa0fhzd3hhpedm30ys4ct8dpelwz3nuqpr4mhxue69uhkymmnw3ezucnfw33k76tww3ux76m09e3k7mf0qgs8a474cw4lqmapcq8hr7res4nknar2ey34fsffk0k42cjsdyn7yqqrqsqqqqqpnn3znl
-
 @ 6d5c826a:4b27b659
2025-05-23 21:43:55
@ 6d5c826a:4b27b659
2025-05-23 21:43:55- Ceph - Distributed object, block, and file storage platform. (Source Code)
LGPL-3.0C++ - DRBD - Distributed replicated storage system, implemented as a Linux kernel driver. (Source Code)
GPL-2.0C - GlusterFS - Software-defined distributed storage that can scale to several petabytes, with interfaces for object, block and file storage. (Source Code)
GPL-2.0/LGPL-3.0C - Hadoop Distributed Filesystem (HDFS) - Distributed file system that provides high-throughput access to application data. (Source Code)
Apache-2.0Java - JuiceFS - Distributed POSIX file system built on top of Redis and S3. (Source Code)
Apache-2.0Go - Kubo - Implementation of IPFS, a global, versioned, peer-to-peer filesystem that seeks to connect all computing devices with the same system of files.
Apache-2.0/MITGo - LeoFS - Highly available, distributed, replicated eventually consistent object/blob store. (Source Code)
Apache-2.0Erlang - Lustre - Parallel distributed file system, generally used for large-scale cluster computing. (Source Code)
GPL-2.0C - Minio - High-performance, S3 compatible object store built for large scale AI/ML, data lake and database workloads. (Source Code)
AGPL-3.0Go - MooseFS - Fault tolerant, network distributed file system. (Source Code)
GPL-2.0C - OpenAFS - Distributed network file system with read-only replicas and multi-OS support. (Source Code)
IPL-1.0C - Openstack Swift - A highly available, distributed, eventually consistent object/blob store. (Source Code)
Apache-2.0Python - Perkeep - A set of open source formats, protocols, and software for modeling, storing, searching, sharing and synchronizing data (previously Camlistore). (Source Code)
Apache-2.0C - TahoeLAFS - Secure, decentralized, fault-tolerant, peer-to-peer distributed data store and distributed file system. (Source Code)
GPL-2.0Python - XtreemFS - Distributed, replicated and fault-tolerant file system for federated IT infrastructures.. (Source Code)
BSD-3-ClauseJava
- Ceph - Distributed object, block, and file storage platform. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:43:37
@ 6d5c826a:4b27b659
2025-05-23 21:43:37- Diagrams.net - A.K.A. Draw.io. Easy to use Diagram UI with a plethora of templates. (Source Code)
Apache-2.0JavaScript/Docker - Kroki - API for generating diagrams from textual descriptions. (Source Code)
MITJava - Mermaid - Javascript module with a unique, easy, shorthand syntax. Integrates into several other tools like Grafana. (Source Code)
MITNodejs/Docker
- Diagrams.net - A.K.A. Draw.io. Easy to use Diagram UI with a plethora of templates. (Source Code)
-
 @ 0e9491aa:ef2adadf
2025-05-24 06:01:20
@ 0e9491aa:ef2adadf
2025-05-24 06:01:20
The newly proposed RESTRICT ACT - is being advertised as a TikTok Ban, but is much broader than that, carries a $1M Fine and up to 20 years in prison️! It is unconstitutional and would create massive legal restrictions on the open source movement and free speech throughout the internet.
The Bill was proposed by: Senator Warner, Senator Thune, Senator Baldwin, Senator Fischer, Senator Manchin, Senator Moran, Senator Bennet, Senator Sullivan, Senator Gillibrand, Senator Collins, Senator Heinrich, and Senator Romney. It has broad support across Senators of both parties.
Corrupt politicians will not protect us. They are part of the problem. We must build, support, and learn how to use censorship resistant tools in order to defend our natural rights.
The RESTRICT Act, introduced by Senators Warner and Thune, aims to block or disrupt transactions and financial holdings involving foreign adversaries that pose risks to national security. Although the primary targets of this legislation are companies like Tik-Tok, the language of the bill could potentially be used to block or disrupt cryptocurrency transactions and, in extreme cases, block Americans’ access to open source tools or protocols like Bitcoin.
The Act creates a redundant regime paralleling OFAC without clear justification, it significantly limits the ability for injured parties to challenge actions raising due process concerns, and unlike OFAC it lacks any carve-out for protected speech. COINCENTER ON THE RESTRICT ACT
If you found this post helpful support my work with bitcoin.

-
 @ 5144fe88:9587d5af
2025-05-23 17:01:37
@ 5144fe88:9587d5af
2025-05-23 17:01:37The recent anomalies in the financial market and the frequent occurrence of world trade wars and hot wars have caused the world's political and economic landscape to fluctuate violently. It always feels like the financial crisis is getting closer and closer.
This is a systematic analysis of the possibility of the current global financial crisis by Manus based on Ray Dalio's latest views, US and Japanese economic and financial data, Buffett's investment behavior, and historical financial crises.
Research shows that the current financial system has many preconditions for a crisis, especially debt levels, market valuations, and investor behavior, which show obvious crisis signals. The probability of a financial crisis in the short term (within 6-12 months) is 30%-40%,
in the medium term (within 1-2 years) is 50%-60%,
in the long term (within 2-3 years) is 60%-70%.
Japan's role as the world's largest holder of overseas assets and the largest creditor of the United States is particularly critical. The sharp appreciation of the yen may be a signal of the return of global safe-haven funds, which will become an important precursor to the outbreak of a financial crisis.
Potential conditions for triggering a financial crisis Conditions that have been met 1. High debt levels: The debt-to-GDP ratio of the United States and Japan has reached a record high. 2. Market overvaluation: The ratio of stock market to GDP hits a record high 3. Abnormal investor behavior: Buffett's cash holdings hit a record high, with net selling for 10 consecutive quarters 4. Monetary policy shift: Japan ends negative interest rates, and the Fed ends the rate hike cycle 5. Market concentration is too high: a few technology stocks dominate market performance
Potential trigger points 1. The Bank of Japan further tightens monetary policy, leading to a sharp appreciation of the yen and the return of overseas funds 2. The US debt crisis worsens, and the proportion of interest expenses continues to rise to unsustainable levels 3. The bursting of the technology bubble leads to a collapse in market confidence 4. The trade war further escalates, disrupting global supply chains and economic growth 5. Japan, as the largest creditor of the United States, reduces its holdings of US debt, causing US debt yields to soar
Analysis of the similarities and differences between the current economic environment and the historical financial crisis Debt level comparison Current debt situation • US government debt to GDP ratio: 124.0% (December 2024) • Japanese government debt to GDP ratio: 216.2% (December 2024), historical high 225.8% (March 2021) • US total debt: 36.21 trillion US dollars (May 2025) • Japanese debt/GDP ratio: more than 250%-263% (Japanese Prime Minister’s statement)
Before the 2008 financial crisis • US government debt to GDP ratio: about 64% (2007) • Japanese government debt to GDP ratio: about 175% (2007)
Before the Internet bubble in 2000 • US government debt to GDP ratio: about 55% (1999) • Japanese government debt to GDP ratio: about 130% (1999)
Key differences • The current US debt-to-GDP ratio is nearly twice that before the 2008 crisis • The current Japanese debt-to-GDP ratio is more than 1.2 times that before the 2008 crisis • Global debt levels are generally higher than historical pre-crisis levels • US interest payments are expected to devour 30% of fiscal revenue (Moody's warning)
Monetary policy and interest rate environment
Current situation • US 10-year Treasury yield: about 4.6% (May 2025) • Bank of Japan policy: end negative interest rates and start a rate hike cycle • Bank of Japan's holdings of government bonds: 52%, plans to reduce purchases to 3 trillion yen per month by January-March 2026 • Fed policy: end the rate hike cycle and prepare to cut interest rates
Before the 2008 financial crisis • US 10-year Treasury yield: about 4.5%-5% (2007) • Fed policy: continuous rate hikes from 2004 to 2006, and rate cuts began in 2007 • Bank of Japan policy: maintain ultra-low interest rates
Key differences • Current US interest rates are similar to those before the 2008 crisis, but debt levels are much higher than then • Japan is in the early stages of ending its loose monetary policy, unlike before historical crises • The size of global central bank balance sheets is far greater than at any time in history
Market valuations and investor behavior Current situation • The ratio of stock market value to the size of the US economy: a record high • Buffett's cash holdings: $347 billion (28% of assets), a record high • Market concentration: US stock growth mainly relies on a few technology giants • Investor sentiment: Technology stocks are enthusiastic, but institutional investors are beginning to be cautious
Before the 2008 financial crisis • Buffett's cash holdings: 25% of assets (2005) • Market concentration: Financial and real estate-related stocks performed strongly • Investor sentiment: The real estate market was overheated and subprime products were widely popular
Before the 2000 Internet bubble • Buffett's cash holdings: increased from 1% to 13% (1998) • Market concentration: Internet stocks were extremely highly valued • Investor sentiment: Tech stocks are in a frenzy
Key differences • Buffett's current cash holdings exceed any pre-crisis level in history • Market valuation indicators have reached a record high, exceeding the levels before the 2000 bubble and the 2008 crisis • The current market concentration is higher than any period in history, and a few technology stocks dominate market performance
Safe-haven fund flows and international relations Current situation • The status of the yen: As a safe-haven currency, the appreciation of the yen may indicate a rise in global risk aversion • Trade relations: The United States has imposed tariffs on Japan, which is expected to reduce Japan's GDP growth by 0.3 percentage points in fiscal 2025 • International debt: Japan is one of the largest creditors of the United States
Before historical crises • Before the 2008 crisis: International capital flows to US real estate and financial products • Before the 2000 bubble: International capital flows to US technology stocks
Key differences • Current trade frictions have intensified and the trend of globalization has weakened • Japan's role as the world's largest holder of overseas assets has become more prominent • International debt dependence is higher than any period in history
-
 @ 6d5c826a:4b27b659
2025-05-23 21:43:11
@ 6d5c826a:4b27b659
2025-05-23 21:43:11- Capistrano - Deploy your application to any number of machines simultaneously, in sequence or as a rolling set via SSH (rake based). (Source Code)
MITRuby - CloudSlang - Flow-based orchestration tool for managing deployed applications, with Docker capabilities. (Source Code)
Apache-2.0Java - CloudStack - Cloud computing software for creating, managing, and deploying infrastructure cloud services. (Source Code)
Apache-2.0Java/Python - Cobbler - Cobbler is a Linux installation server that allows for rapid setup of network installation environments. (Source Code)
GPL-2.0Python - Fabric - Python library and cli tool for streamlining the use of SSH for application deployment or systems administration tasks. (Source Code)
BSD-2-ClausePython - Genesis - A template framework for multi-environment BOSH deployments.
MITPerl - munki - Webserver-based repository of packages and package metadata, that allows macOS administrators to manage software installs. (Source Code)
Apache-2.0Python - Overcast - Deploy VMs across different cloud providers, and run commands and scripts across any or all of them in parallel via SSH. (Source Code)
MITNodejs
- Capistrano - Deploy your application to any number of machines simultaneously, in sequence or as a rolling set via SSH (rake based). (Source Code)
-
 @ c1e9ab3a:9cb56b43
2025-05-05 14:25:28
@ c1e9ab3a:9cb56b43
2025-05-05 14:25:28Introduction: The Power of Fiction and the Shaping of Collective Morality
Stories define the moral landscape of a civilization. From the earliest mythologies to the modern spectacle of global cinema, the tales a society tells its youth shape the parameters of acceptable behavior, the cost of transgression, and the meaning of justice, power, and redemption. Among the most globally influential narratives of the past half-century is the Star Wars saga, a sprawling science fiction mythology that has transcended genre to become a cultural religion for many. Central to this mythos is the arc of Anakin Skywalker, the fallen Jedi Knight who becomes Darth Vader. In Star Wars: Episode III – Revenge of the Sith, Anakin commits what is arguably the most morally abhorrent act depicted in mainstream popular cinema: the mass murder of children. And yet, by the end of the saga, he is redeemed.
This chapter introduces the uninitiated to the events surrounding this narrative turn and explores the deep structural and ethical concerns it raises. We argue that the cultural treatment of Darth Vader as an anti-hero, even a role model, reveals a deep perversion in the collective moral grammar of the modern West. In doing so, we consider the implications this mythology may have on young adults navigating identity, masculinity, and agency in a world increasingly shaped by spectacle and symbolic narrative.
Part I: The Scene and Its Context
In Revenge of the Sith (2005), the third episode of the Star Wars prequel trilogy, the protagonist Anakin Skywalker succumbs to fear, ambition, and manipulation. Convinced that the Jedi Council is plotting against the Republic and desperate to save his pregnant wife from a vision of death, Anakin pledges allegiance to Chancellor Palpatine, secretly the Sith Lord Darth Sidious. Upon doing so, he is given a new name—Darth Vader—and tasked with a critical mission: to eliminate all Jedi in the temple, including its youngest members.
In one of the most harrowing scenes in the film, Anakin enters the Jedi Temple. A group of young children, known as "younglings," emerge from hiding and plead for help. One steps forward, calling him "Master Skywalker," and asks what they are to do. Anakin responds by igniting his lightsaber. The screen cuts away, but the implication is unambiguous. Later, it is confirmed through dialogue and visual allusion that he slaughtered them all.
There is no ambiguity in the storytelling. The man who will become the galaxy’s most feared enforcer begins his descent by murdering defenseless children.
Part II: A New Kind of Evil in Youth-Oriented Media
For decades, cinema avoided certain taboos. Even films depicting war, genocide, or psychological horror rarely crossed the line into showing children as victims of deliberate violence by the protagonist. When children were harmed, it was by monstrous antagonists, supernatural forces, or offscreen implications. The killing of children was culturally reserved for historical atrocities and horror tales.
In Revenge of the Sith, this boundary was broken. While the film does not show the violence explicitly, the implication is so clear and so central to the character arc that its omission from visual depiction does not blunt the narrative weight. What makes this scene especially jarring is the tonal dissonance between the gravity of the act and the broader cultural treatment of Star Wars as a family-friendly saga. The juxtaposition of child-targeted marketing with a central plot involving child murder is not accidental—it reflects a deeper narrative and commercial structure.
This scene was not a deviation from the arc. It was the intended turning point.
Part III: Masculinity, Militarism, and the Appeal of the Anti-Hero
Darth Vader has long been idolized as a masculine icon. His towering presence, emotionless control, and mechanical voice exude power and discipline. Military institutions have quoted him. He is celebrated in memes, posters, and merchandise. Within the cultural imagination, he embodies dominance, command, and strategic ruthlessness.
For many young men, particularly those struggling with identity, agency, and perceived weakness, Vader becomes more than a character. He becomes an archetype: the man who reclaims power by embracing discipline, forsaking emotion, and exacting vengeance against those who betrayed him. The emotional pain that leads to his fall mirrors the experiences of isolation and perceived emasculation that many young men internalize in a fractured society.
The symbolism becomes dangerous. Anakin's descent into mass murder is portrayed not as the outcome of unchecked cruelty, but as a tragic mistake rooted in love and desperation. The implication is that under enough pressure, even the most horrific act can be framed as a step toward a noble end.
Part IV: Redemption as Narrative Alchemy
By the end of the original trilogy (Return of the Jedi, 1983), Darth Vader kills the Emperor to save his son Luke and dies shortly thereafter. Luke mourns him, honors him, and burns his body in reverence. In the final scene, Vader's ghost appears alongside Obi-Wan Kenobi and Yoda—the very men who once considered him the greatest betrayal of their order. He is welcomed back.
There is no reckoning. No mention of the younglings. No memorial to the dead. No consequence beyond his own internal torment.
This model of redemption is not uncommon in Western storytelling. In Christian doctrine, the concept of grace allows for any sin to be forgiven if the sinner repents sincerely. But in the context of secular mass culture, such redemption without justice becomes deeply troubling. The cultural message is clear: even the worst crimes can be erased if one makes a grand enough gesture at the end. It is the erasure of moral debt by narrative fiat.
The implication is not only that evil can be undone by good, but that power and legacy matter more than the victims. Vader is not just forgiven—he is exalted.
Part V: Real-World Reflections and Dangerous Scripts
In recent decades, the rise of mass violence in schools and public places has revealed a disturbing pattern: young men who feel alienated, betrayed, or powerless adopt mythic narratives of vengeance and transformation. They often see themselves as tragic figures forced into violence by a cruel world. Some explicitly reference pop culture, quoting films, invoking fictional characters, or modeling their identities after cinematic anti-heroes.
It would be reductive to claim Star Wars causes such events. But it is equally naive to believe that such narratives play no role in shaping the symbolic frameworks through which vulnerable individuals understand their lives. The story of Anakin Skywalker offers a dangerous script:
- You are betrayed.
- You suffer.
- You kill.
- You become powerful.
- You are redeemed.
When combined with militarized masculinity, institutional failure, and cultural nihilism, this script can validate the darkest impulses. It becomes a myth of sacrificial violence, with the perpetrator as misunderstood hero.
Part VI: Cultural Responsibility and Narrative Ethics
The problem is not that Star Wars tells a tragic story. Tragedy is essential to moral understanding. The problem is how the culture treats that story. Darth Vader is not treated as a warning, a cautionary tale, or a fallen angel. He is merchandised, celebrated, and decontextualized.
By separating his image from his actions, society rebrands him as a figure of cool dominance rather than ethical failure. The younglings are forgotten. The victims vanish. Only the redemption remains. The merchandise continues to sell.
Cultural institutions bear responsibility for how such narratives are presented and consumed. Filmmakers may intend nuance, but marketing departments, military institutions, and fan cultures often reduce that nuance to symbol and slogan.
Conclusion: Reckoning with the Stories We Tell
The story of Anakin Skywalker is not morally neutral. It is a tale of systemic failure, emotional collapse, and unchecked violence. When presented in full, it can serve as a powerful warning. But when reduced to aesthetic dominance and easy redemption, it becomes a tool of moral decay.
The glorification of Darth Vader as a cultural icon—divorced from the horrific acts that define his transformation—is not just misguided. It is dangerous. It trains a generation to believe that power erases guilt, that violence is a path to recognition, and that final acts of loyalty can overwrite the deliberate murder of the innocent.
To the uninitiated, Star Wars may seem like harmless fantasy. But its deepest myth—the redemption of the child-killer through familial love and posthumous honor—deserves scrutiny. Not because fiction causes violence, but because fiction defines the possibilities of how we understand evil, forgiveness, and what it means to be a hero.
We must ask: What kind of redemption erases the cries of murdered children? And what kind of culture finds peace in that forgetting?
-
 @ cae03c48:2a7d6671
2025-05-23 16:01:05
@ cae03c48:2a7d6671
2025-05-23 16:01:05Bitcoin Magazine
Spark Partners with Breez to Launch Bitcoin-Native SDK for Lightning PaymentsToday, Breez and Spark have announced a new implementation of the Breez SDK, built on Spark’s Bitcoin-native Layer 2 infrastructure. According to a press release sent to Bitcoin Magazine, the update is intended to make it easier for developers to integrate self-custodial Bitcoin Lightning payments into everyday apps and services.
Few companies are as good as @Breez_Tech at putting Bitcoin in people’s hands. We’re incredibly humbled to have them building on Spark.
Learn more → https://t.co/KRPpWJa3os pic.twitter.com/QiCfHbWu9d
— Spark (@buildonspark) May 22, 2025
“This is what the future of Bitcoin looks like — fast, open, and embedded in the apps people use every day. By teaming up with Breez, we’re expanding the ecosystem and giving developers powerful, Bitcoin-native tools to build next-generation payment experiences. Together, we’re building the standard for global, peer-to-peer transactions,” said the creator of Spark Kevin Hurley.
The SDK supports LNURL, Lightning addresses, real-time mobile notifications, and includes bindings for all major programming languages and frameworks. It is designed to allow developers to build directly on Bitcoin without relying on bridges or external consensus. This collaboration gives developers tools to add Bitcoin payment features to apps used for monetization social apps, cross-border remittances, and in-game currencies.
“We need developers to bring Bitcoin into apps people use every day,” said the CEO of Breez Roy Sheinfeld. “That’s why we built the Breez SDK. We’re excited to build on Spark’s revolutionary architecture — giving developers a powerful new Bitcoin-native option and continuing to strengthen Lightning as the common language of Bitcoin.”
Breez will also operate as a Spark Service Provider (SSP), alongside Lightspark, to help support payment facilitation and the growth of Spark’s ecosystem. The new implementation is expected to be released later this year.
“We’re excited to see what developers build with Spark; it’s very exciting to see this come to the world,” said the co-founder and CEO of Lightspark David Marcus.
The Breez SDK is expanding

We’re joining forces with @buildonspark to release a new nodeless implementation of the Breez SDK — giving developers the tools they need to bring Bitcoin payments to everyday apps.
Bitcoin-Native
Powered by Spark’s…— Breez
 (@Breez_Tech) May 22, 2025
(@Breez_Tech) May 22, 2025Yesterday, Magic Eden also partnered with Spark to improve Bitcoin trading by addressing issues like slow transaction times, high fees, and poor user experience. The integration will introduce a native settlement system aimed at making transactions faster and more cost-effective, without using bridges or synthetic assets.
“We’re proud to be betting on BTC DeFi,” said the CEO of Magic Eden Jack Lu. “We’re going to lead the forefront of all Bitcoin DeFi to make BTC fast, fun, and for everyone with Magic Eden as the #1 BTC native app on-chain.”
This post Spark Partners with Breez to Launch Bitcoin-Native SDK for Lightning Payments first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:42:54
@ 6d5c826a:4b27b659
2025-05-23 21:42:54- Ajenti - Control panel for Linux and BSD. (Source Code)
MITPython/Shell - Cockpit - Web-based graphical interface for servers. (Source Code)
LGPL-2.1C - Froxlor - Lightweight server management software with Nginx and PHP-FPM support. (Source Code)
GPL-2.0PHP - HestiaCP - Web server control panel (fork of VestaCP). (Demo, Source Code)
GPL-3.0PHP/Shell/Other - ISPConfig - Manage Linux servers directly through your browser. (Source Code)
BSD-3-ClausePHP - Sentora - Open-Source Web hosting control panel for Linux, BSD (fork of ZPanel). (Source Code)
GPL-3.0PHP - Virtualmin - Powerful and flexible web hosting control panel for Linux and BSD systems. (Source Code)
GPL-3.0Shell/Perl/Other - Webmin - Web-based interface for system administration for Unix. (Source Code)
BSD-3-ClausePerl
- Ajenti - Control panel for Linux and BSD. (Source Code)
-
 @ 146904a0:890e2a2f
2025-05-23 22:47:55
@ 146904a0:890e2a2f
2025-05-23 22:47:55How Bukele’s bold bitcoin move gained global attention but left the public behind
In a quiet coastal town called El Zonte, where dusty streets meet ocean waves, an amazing experiment began in 2019. A Christian surfer named Mike Peterson arrived with an anonymous bitcoin donation, given with one condition: it must be used only in bitcoin.
This sparked the birth of Bitcoin Beach, a micro-economy powered by Bitcoin, and unknowingly laid the groundwork for the most radical financial experiment ever attempted by a government.
At the Bitcoin 2021 Conference in Miami, El Salvador’s president, Nayib Bukele, appeared via video, making a shocking announcement: his country, El Salvador, would become the first in the world to adopt bitcoin as legal tender.
Just three days later in under five hours, with no public consultation or economic analysis. The Bitcoin Law was approved by El Salvador’s Legislative Assembly—This happened shortly after Bukele had removed the Constitutional Court and Attorney General, effectively eliminating institutional checks.
The government launched its official digital wallet: Chivo Wallet, offering $30 in bitcoin to every citizen who downloaded and registered.
But what was promised as a financial revolution quickly turned chaotic:
-
The app was riddled with technical failures.
-
Thousands of Salvadorans couldn’t access their funds.
-
Identity theft became rampant, with fake accounts created to fraudulently claim the bonus.
Public confidence plummeted, and trust disappeared. For most Salvadorans, bitcoin became a ghost.
According to verified reports:
-
$150M went to a conversion fund ( liquidity for the Chivo wallet)
-
$30M to the Chivo bonus
-
$23.3M to ATMs and infrastructure
-
$2M to marketing and tools
With total cost above $200M USD.
Meanwhile, no audit has ever been released, and most government data is classified.
What did the Salvadoran people get?
-
79% of Salvadorans never used Bitcoin after taking their 30 USD out of the Chivo wallet.
-
Only 10% of businesses accept it
-
Remittances via BTC? Just 1.5% of the total
-
Foreign investment? It actually dropped after the rollout
But yet in El Zonte, where "the bitcoin beach" is located, locals are now being pushed out as land prices soar. A luxury Bitcoin Beach Club is evicting families. The town that started it all is now being sold off—one beach front at a time.
But Bukele won the spotlight
Bitcoin was born as open-source money—neutral, permission-less, and voluntary. No Bitcoiner came to it by force; we each arrived for our own reasons: financial sovereignty, censorship resistance, or simple curiosity. That spirit of freedom stands in sharp contrast to any top-down attempt to impose it on an entire population.
In January 29 2025, El Salvador’s Legislative Assembly hurried through a set of amendments to the 2021 Bitcoin Law. The reform scrapped the mandate that every merchant must accept BTC and removed bitcoin’s status as legal tender, turning it into an optional payment instrument.
Those changes came just days before the IMF approved a US $1.4 billion Extended Fund Facility. The new agreement explicitly required “unwinding” state participation in Chivo and dropping bitcoin as legal tender.
Bukele once framed bitcoin as a symbol of “financial freedom,” yet the 2025 rollback shows the opposite: His government needed Bitcoin’s headline power more than Bitcoin needed state endorsement. True adoption will come, if it comes at all, because Salvadorans choose it—just as millions worldwide already do—not because a decree tells them to.
While the people saw few benefits, Bukele gained international fame. He became the “Bitcoin President,” speaking at conferences, meeting with bitcoin whales, and podcasters, positioning El Salvador as a bitcoin paradise. This is far from reality. The legal tender label is gone, but El Salvador’s citizens remain free to experiment with BTC on their own terms—and many eventually will.
Sources:
-
Bukele: El Señor de los Sueños – Ep. 4\ Produced by: Central Podcast & Radio Ambulante Studios
-
reported by Silvia Biñas and Gabriel Labrador
-
Official transcript: centralpodcast.audio/transcripcion/episodio-4
-
Verified data from FES, Yahoo Finance.
-
-
 @ 90152b7f:04e57401
2025-05-23 15:48:58
@ 90152b7f:04e57401
2025-05-23 15:48:58U.S. troops would enforce peace under Army study
The Washington Times - September 10, 2001
by Rowan Scarborough
https://www.ord.io/70787305 (image) https://www.ord.io/74522515 (text)
An elite U.S. Army study center has devised a plan for enforcing a major Israeli-Palestinian peace accord that would require about 20,000 well-armed troops stationed throughout Israel and a newly created Palestinian state. There are no plans by the Bush administration to put American soldiers into the Middle East to police an agreement forged by the longtime warring parties. In fact, Defense Secretary Donald H. Rumsfeld is searching for ways to reduce U.S. peacekeeping efforts abroad, rather than increasing such missions. But a 68-page paper by the Army School of Advanced Military Studies (SAMS) does provide a look at the daunting task any international peacekeeping force would face if the United Nations authorized it, and Israel and the Palestinians ever reached a peace agreement.
Located at Fort Leavenworth, Kan., the School for Advanced Military Studies is both a training ground and a think tank for some of the Army’s brightest officers. Officials say the Army chief of staff, and sometimes the Joint Chiefs of Staff, ask SAMS to develop contingency plans for future military operations. During the 1991 Persian Gulf war, SAMS personnel helped plan the coalition ground attack that avoided a strike up the middle of Iraqi positions and instead executed a “left hook” that routed the enemy in 100 hours.
The cover page for the recent SAMS project said it was done for the Joint Chiefs of Staff. But Maj. Chris Garver, a Fort Leavenworth spokesman, said the study was not requested by Washington. “This was just an academic exercise,” said Maj. Garver. “They were trying to take a current situation and get some training out of it.” The exercise was done by 60 officers dubbed “Jedi Knights,” as all second-year SAMS students are nicknamed.
The SAMS paper attempts to predict events in the first year of a peace-enforcement operation, and sees possible dangers for U.S. troops from both sides. It calls Israel’s armed forces a “500-pound gorilla in Israel. Well armed and trained. Operates in both Gaza . Known to disregard international law to accomplish mission. Very unlikely to fire on American forces. Fratricide a concern especially in air space management.”
Of the Mossad, the Israeli intelligence service, the SAMS officers say: “Wildcard. Ruthless and cunning. Has capability to target U.S. forces and make it look like a Palestinian/Arab act.”
On the Palestinian side, the paper describes their youth as “loose cannons; under no control, sometimes violent.” The study lists five Arab terrorist groups that could target American troops for assassination and hostage-taking. The study recommends “neutrality in word and deed” as one way to protect U.S. soldiers from any attack. It also says Syria, Egypt and Jordan must be warned “we will act decisively in response to external attack.”
It is unlikely either of the three would mount an attack. Of Syria’s military, the report says: “Syrian army quantitatively larger than Israeli Defense Forces, but largely seen as qualitatively inferior. More likely, however, Syrians would provide financial and political support to the Palestinians, as well as increase covert support to terrorism acts through Lebanon.” Of Egypt’s military, the paper says, “Egyptians also maintain a large army but have little to gain by attacking Israel.”
The plan does not specify a full order of battle. An Army source who reviewed the SAMS work said each of a possible three brigades would require about 100 Bradley fighting vehicles, 25 tanks, 12 self-propelled howitzers, Apache attack helicopters, Kiowa Warrior reconnaissance helicopters and Predator spy drones. The report predicts that nonlethal weapons would be used to quell unrest. U.S. European Command, which is headed by NATO’s supreme allied commander, would oversee the peacekeeping operation. Commanders would maintain areas of operation, or AOs, around Nablus, Jerusalem, Hebron and the Gaza strip. The study sets out a list of goals for U.S. troops to accomplish in the first 30 days. They include: “create conditions for development of Palestinian State and security of “; ensure “equal distribution of contract value or equivalent aid” that would help legitimize the peacekeeping force and stimulate economic growth; “promote U.S. investment in Palestine”; “encourage reconciliation between entities based on acceptance of new national identities”; and “build lasting relationship based on new legal borders and not religious-territorial claims.”
Maj. Garver said the officers who completed the exercise will hold major planning jobs once they graduate. “There is an application process” for students, he said. “They screen their records, and there are several tests they go through before they are accepted by the program. The bright planners of the future come out of this program.”
James Phillips, a Middle East analyst at the Heritage Foundation, said it would be a mistake to put peacekeepers in Israel, given the “poor record of previous monitors.” “In general, the Bush administration policy is to discourage a large American presence,” he said. “But it has been rumored that one of the possibilities might be an expanded CIA role.” “It would be a very different environment than Bosnia,” said Mr. Phillips, referring to America’s six-year peacekeeping role in Bosnia-Herzegovina. “The Palestinian Authority is pushing for this as part of its strategy to internationalize the conflict. Bring in the Europeans and Russia and China. But such monitors or peacekeeping forces are not going to be able to bring peace. Only a decision by the Palestinians to stop the violence and restart talks could possibly do that.”
<<https://www.ord.io/70787305>>
<<<https://www.ord.io/74522515>>>
-
 @ dfa02707:41ca50e3
2025-05-24 06:01:00
@ dfa02707:41ca50e3
2025-05-24 06:01:00Contribute to keep No Bullshit Bitcoin news going.
- The latest firmware updates for COLDCARD devices introduce two major features: COLDCARD Co-sign (CCC) and Key Teleport between two COLDCARD Q devices using QR codes and/or NFC with a website.
What's new
- COLDCARD Co-Sign: When CCC is enabled, a second seed called the Spending Policy Key (Key C) is added to the device. This seed works with the device's Main Seed and one or more additional XPUBs (Backup Keys) to form 2-of-N multisig wallets.
- The spending policy functions like a hardware security module (HSM), enforcing rules such as magnitude and velocity limits, address whitelisting, and 2FA authentication to protect funds while maintaining flexibility and control, and is enforced each time the Spending Policy Key is used for signing.
- When spending conditions are met, the COLDCARD signs the partially signed bitcoin transaction (PSBT) with the Main Seed and Spending Policy Key for fund access. Once configured, the Spending Policy Key is required to view or change the policy, and violations are denied without explanation.
"You can override the spending policy at any time by signing with either a Backup Key and the Main Seed or two Backup Keys, depending on the number of keys (N) in the multisig."
-
A step-by-step guide for setting up CCC is available here.
-
Key Teleport for Q devices allows users to securely transfer sensitive data such as seed phrases (words, xprv), secure notes and passwords, and PSBTs for multisig. It uses QR codes or NFC, along with a helper website, to ensure reliable transmission, keeping your sensitive data protected throughout the process.
- For more technical details, see the protocol spec.
"After you sign a multisig PSBT, you have option to “Key Teleport” the PSBT file to any one of the other signers in the wallet. We already have a shared pubkey with them, so the process is simple and does not require any action on their part in advance. Plus, starting in this firmware release, COLDCARD can finalize multisig transactions, so the last signer can publish the signed transaction via PushTX (NFC tap) to get it on the blockchain directly."
- Multisig transactions are finalized when sufficiently signed. It streamlines the use of PushTX with multisig wallets.
- Signing artifacts re-export to various media. Users are now provided with the capability to export signing products, like transactions or PSBTs, to alternative media rather than the original source. For example, if a PSBT is received through a QR code, it can be signed and saved onto an SD card if needed.
- Multisig export files are signed now. Public keys are encoded as P2PKH address for all multisg signature exports. Learn more about it here.
- NFC export usability upgrade: NFC keeps exporting until CANCEL/X is pressed.
- Added Bitcoin Safe option to Export Wallet.
- 10% performance improvement in USB upload speed for large files.
- Q: Always choose the biggest possible display size for QR.
Fixes
- Do not allow change Main PIN to same value already used as Trick PIN, even if Trick PIN is hidden.
- Fix stuck progress bar under
Receiving...after a USB communications failure. - Showing derivation path in Address Explorer for root key (m) showed double slash (//).
- Can restore developer backup with custom password other than 12 words format.
- Virtual Disk auto mode ignores already signed PSBTs (with “-signed” in file name).
- Virtual Disk auto mode stuck on “Reading…” screen sometimes.
- Finalization of foreign inputs from partial signatures. Thanks Christian Uebber!
- Temporary seed from COLDCARD backup failed to load stored multisig wallets.
Destroy Seedalso removes all Trick PINs from SE2.Lock Down Seedrequires pressing confirm key (4) to execute.- Q only: Only BBQr is allowed to export Coldcard, Core, and pretty descriptor.

-
 @ 6d5c826a:4b27b659
2025-05-23 21:42:36
@ 6d5c826a:4b27b659
2025-05-23 21:42:36- Buildbot - Python-based toolkit for continuous integration. (Source Code)
GPL-2.0Python - CDS - Enterprise-Grade Continuous Delivery & DevOps Automation Open Source Platform. (Source Code)
BSD-3-ClauseGo - Concourse - Concourse is a CI tool that treats pipelines as first class objects and containerizes every step along the way. (Demo, Source Code)
Apache-2.0Go - drone - Drone is a Continuous Delivery platform built on Docker, written in Go. (Source Code)
Apache-2.0Go - Factor - Programmatically define and run workflows to connect configuration management, source code management, build, continuous integration, continuous deployment and communication tools. (Source Code)
MITRuby - GitLab CI - Gitlab's built-in, full-featured CI/CD solution. (Source Code)
MITRuby - GoCD - Continuous delivery server. (Source Code)
Apache-2.0Java/Ruby - Jenkins - Continuous Integration Server. (Source Code)
MITJava - Laminar - Fast, lightweight, simple and flexible Continuous Integration. (Source Code)
GPL-3.0C++ - PHP Censor - Open source self-hosted continuous integration server for PHP projects.
BSD-2-ClausePHP - Strider - Open Source Continuous Deployment / Continuous Integration platform. (Source Code)
MITNodejs - Terrateam - GitOps-first automation platform for Terraform and OpenTofu workflows with support for self-hosted runners. (Source Code)
MPL-2.0OCaml/Docker - werf - Open Source CI/CD tool for building Docker images and deploying to Kubernetes via GitOps. (Source Code)
Apache-2.0Go - Woodpecker - Community fork of Drone that uses Docker containers. (Source Code)
Apache-2.0Go
- Buildbot - Python-based toolkit for continuous integration. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:42:17
@ 6d5c826a:4b27b659
2025-05-23 21:42:17- Collins - At Tumblr, it's the infrastructure source of truth and knowledge. (Source Code)
Apache-2.0Docker/Scala - i-doit - IT Documentation and CMDB.
AGPL-3.0PHP - iTop - Complete ITIL web based service management tool. (Source Code)
AGPL-3.0PHP - netbox - IP address management (IPAM) and data center infrastructure management (DCIM) tool. (Demo, Source Code)
Apache-2.0Python
- Collins - At Tumblr, it's the infrastructure source of truth and knowledge. (Source Code)
-
 @ 87e98bb6:8d6616f4
2025-05-23 15:36:32
@ 87e98bb6:8d6616f4
2025-05-23 15:36:32Use this guide if you want to keep your NixOS on the stable branch, but enable unstable application packages. It took me a while to figure out how to do this, so I wanted to share because it ended up being far easier than most of the vague explanations online made it seem.
I put a sample configuration.nix file at the very bottom to help it make more sense for new users. Remember to keep a backup of your config file, just in case!
If there are any errors please let me know. I am currently running NixOS 24.11.
Steps listed in this guide: 1. Add the unstable channel to NixOS as a secondary channel. 2. Edit the configuration.nix to enable unstable applications. 3. Add "unstable." in front of the application names in the config file (example: unstable.program). This enables the install of unstable versions during the build. 4. Rebuild.
Step 1:
- Open the console. (If you want to see which channels you currently have, type: sudo nix-channel --list)
- Add the unstable channel, type: sudo nix-channel --add https://channels.nixos.org/nixpkgs-unstable unstable
- To update the channels (bring in the possible apps), type: sudo nix-channel --update
More info here: https://nixos.wiki/wiki/Nix_channels
Step 2:
Edit your configuration.nix and add the following around your current config:
``` { config, pkgs, lib, ... }:
let unstable = import
{ config = { allowUnfree = true; }; }; in { #insert normal configuration text here } #remember to close the bracket!```
At this point it would be good to save your config and try a rebuild to make sure there are no errors. If you have errors, make sure your brackets are in the right places and/or not missing. This step will make for less troubleshooting later on if something happens to be in the wrong spot!
Step 3:
Add "unstable." to the start of each application you want to use the unstable version. (Example: unstable.brave)
Step 4:
Rebuild your config, type: sudo nixos-rebuild switch
Example configuration.nix file:
```
Config file for NixOS
{ config, pkgs, lib, ... }:
Enable unstable apps from Nix repository.
let unstable = import
{ config = { allowUnfree = true; }; }; in { #Put your normal config entries here in between the tags. Below is what your applications list needs to look like.
environment.systemPackages = with pkgs; [ appimage-run blender unstable.brave #Just add unstable. before the application name to enable the unstable version. chirp discord ];
} # Don't forget to close bracket at the end of the config file!
``` That should be all. Hope it helps.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:41:59
@ 6d5c826a:4b27b659
2025-05-23 21:41:59- Ansible - Provisioning, configuration management, and application-deployment tool. (Source Code)
GPL-3.0Python - CFEngine - Configuration management system for automated configuration and maintenance of large-scale computer systems. (Source Code)
GPL-3.0C - Chef - Configuration management tool using a pure-Ruby, domain-specific language (DSL) for writing system configuration "recipes". (Source Code)
Apache-2.0Ruby - cloud-init - Initialization tool to automate the configuration of VMs, cloud instances, or machines on a network. (Source Code)
GPL-3.0/Apache-2.0Python - Puppet - Software configuration management tool which includes its own declarative language to describe system configuration. (Source Code)
Apache-2.0Ruby/C - Rudder - Scalable and dynamic configuration management system for patching, security & compliance, based on CFEngine. (Source Code)
GPL-3.0Scala - Salt - Event-driven IT automation, remote task execution, and configuration management software. (Source Code)
Apache-2.0Python
- Ansible - Provisioning, configuration management, and application-deployment tool. (Source Code)
-
 @ 52b4a076:e7fad8bd
2025-05-03 21:54:45
@ 52b4a076:e7fad8bd
2025-05-03 21:54:45Introduction
Me and Fishcake have been working on infrastructure for Noswhere and Nostr.build. Part of this involves processing a large amount of Nostr events for features such as search, analytics, and feeds.
I have been recently developing
nosdexv3, a newer version of the Noswhere scraper that is designed for maximum performance and fault tolerance using FoundationDB (FDB).Fishcake has been working on a processing system for Nostr events to use with NB, based off of Cloudflare (CF) Pipelines, which is a relatively new beta product. This evening, we put it all to the test.
First preparations
We set up a new CF Pipelines endpoint, and I implemented a basic importer that took data from the
nosdexdatabase. This was quite slow, as it did HTTP requests synchronously, but worked as a good smoke test.Asynchronous indexing
I implemented a high-contention queue system designed for highly parallel indexing operations, built using FDB, that supports: - Fully customizable batch sizes - Per-index queues - Hundreds of parallel consumers - Automatic retry logic using lease expiration
When the scraper first gets an event, it will process it and eventually write it to the blob store and FDB. Each new event is appended to the event log.
On the indexing side, a
Queuerwill read the event log, and batch events (usually 2K-5K events) into one work job. This work job contains: - A range in the log to index - Which target this job is intended for - The size of the job and some other metadataEach job has an associated leasing state, which is used to handle retries and prioritization, and ensure no duplication of work.
Several
Workers monitor the index queue (up to 128) and wait for new jobs that are available to lease.Once a suitable job is found, the worker acquires a lease on the job and reads the relevant events from FDB and the blob store.
Depending on the indexing type, the job will be processed in one of a number of ways, and then marked as completed or returned for retries.
In this case, the event is also forwarded to CF Pipelines.
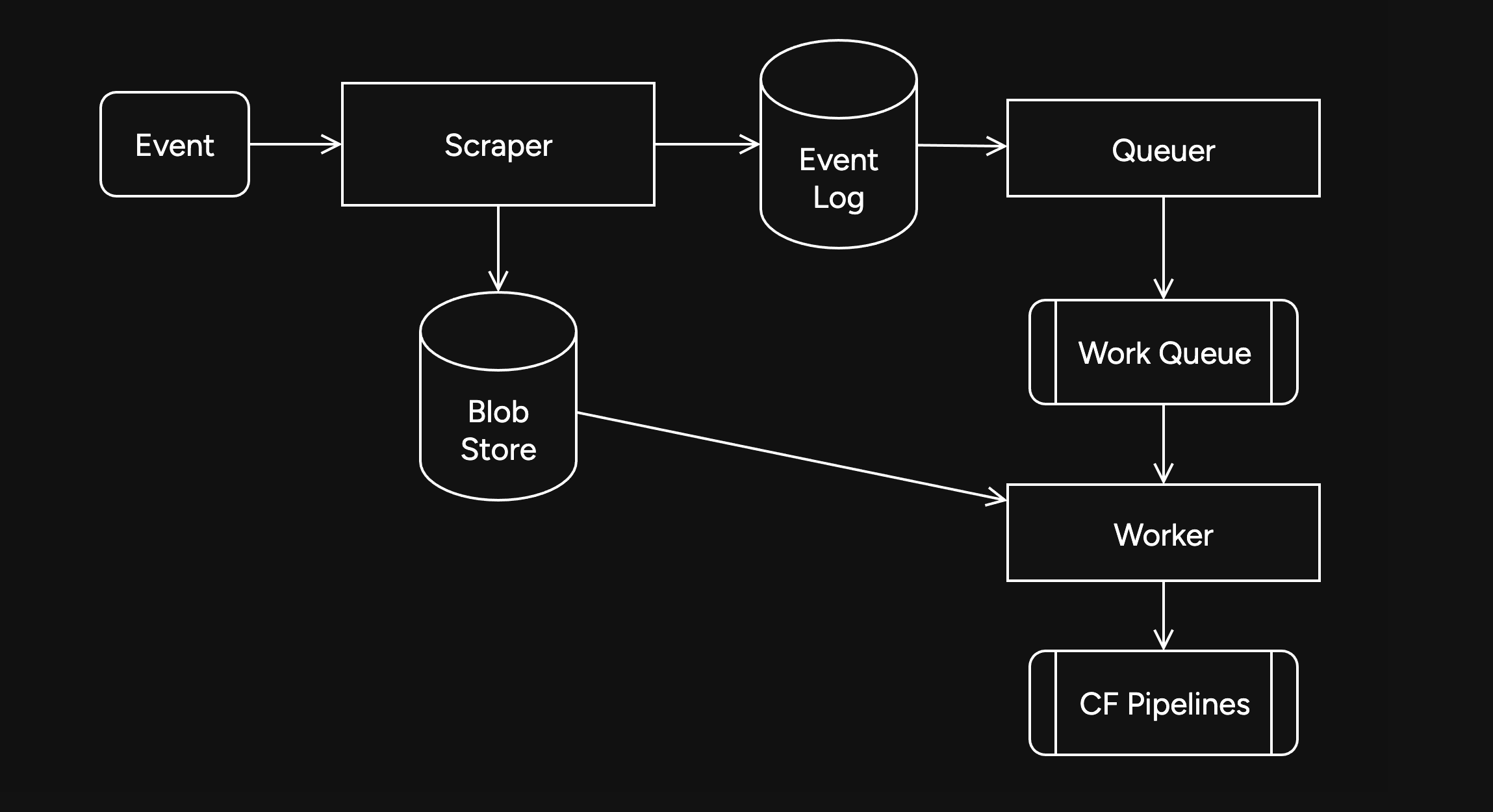
Trying it out
The first attempt did not go well. I found a bug in the high-contention indexer that led to frequent transaction conflicts. This was easily solved by correcting an incorrectly set parameter.
We also found there were other issues in the indexer, such as an insufficient amount of threads, and a suspicious decrease in the speed of the
Queuerduring processing of queued jobs.Along with fixing these issues, I also implemented other optimizations, such as deprioritizing
WorkerDB accesses, and increasing the batch size.To fix the degraded
Queuerperformance, I ran the backfill job by itself, and then started indexing after it had completed.Bottlenecks, bottlenecks everywhere

After implementing these fixes, there was an interesting problem: The DB couldn't go over 80K reads per second. I had encountered this limit during load testing for the scraper and other FDB benchmarks.
As I suspected, this was a client thread limitation, as one thread seemed to be using high amounts of CPU. To overcome this, I created a new client instance for each
Worker.After investigating, I discovered that the Go FoundationDB client cached the database connection. This meant all attempts to create separate DB connections ended up being useless.
Using
OpenWithConnectionStringpartially resolved this issue. (This also had benefits for service-discovery based connection configuration.)To be able to fully support multi-threading, I needed to enabled the FDB multi-client feature. Enabling it also allowed easier upgrades across DB versions, as FDB clients are incompatible across versions:
FDB_NETWORK_OPTION_EXTERNAL_CLIENT_LIBRARY="/lib/libfdb_c.so"FDB_NETWORK_OPTION_CLIENT_THREADS_PER_VERSION="16"Breaking the 100K/s reads barrier
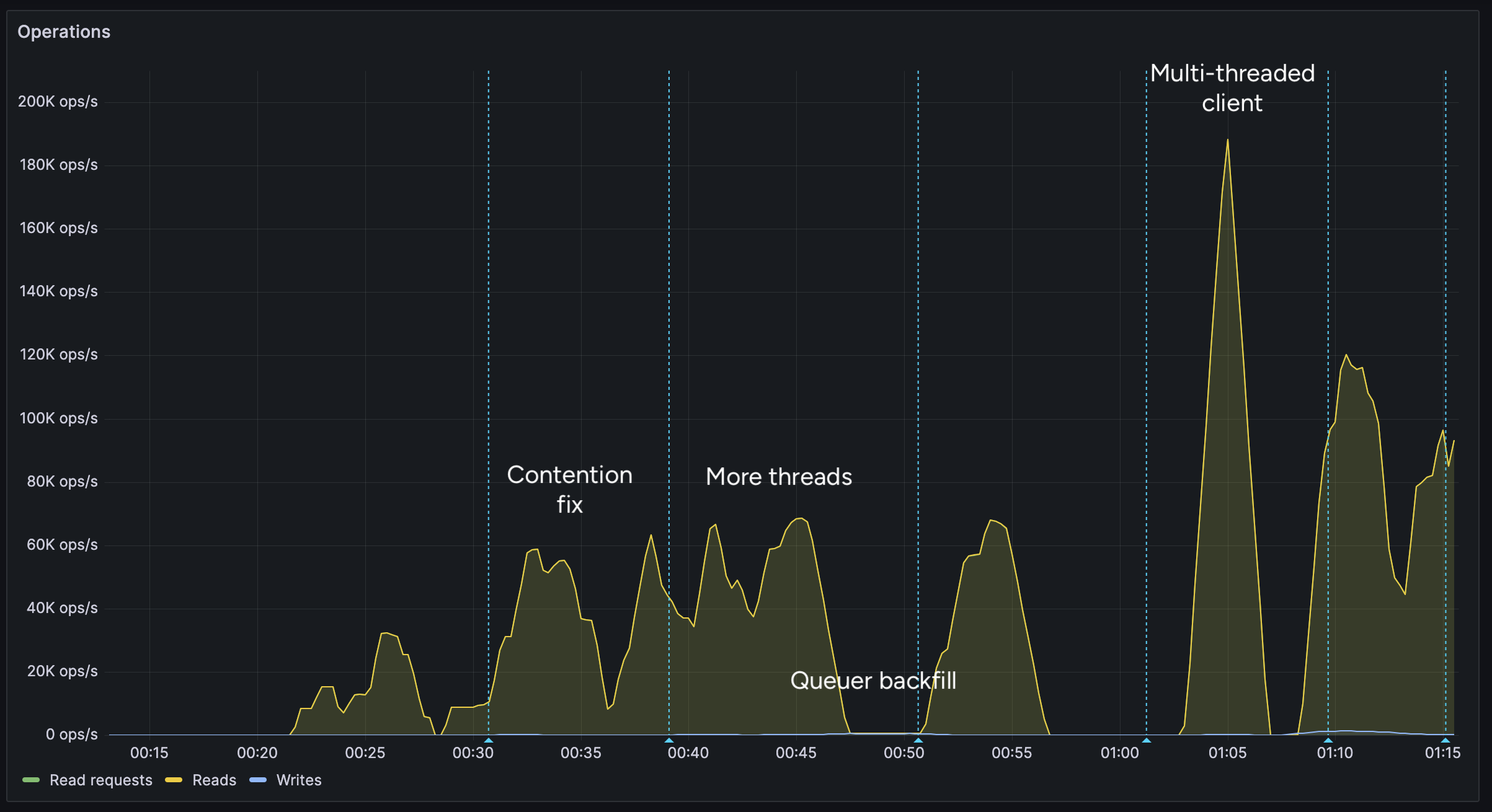
After implementing support for the multi-threaded client, we were able to get over 100K reads per second.
You may notice after the restart (gap) the performance dropped. This was caused by several bugs: 1. When creating the CF Pipelines endpoint, we did not specify a region. The automatically selected region was far away from the server. 2. The amount of shards were not sufficient, so we increased them. 3. The client overloaded a few HTTP/2 connections with too many requests.
I implemented a feature to assign each
Workerits own HTTP client, fixing the 3rd issue. We also moved the entire storage region to West Europe to be closer to the servers.After these changes, we were able to easily push over 200K reads/s, mostly limited by missing optimizations:
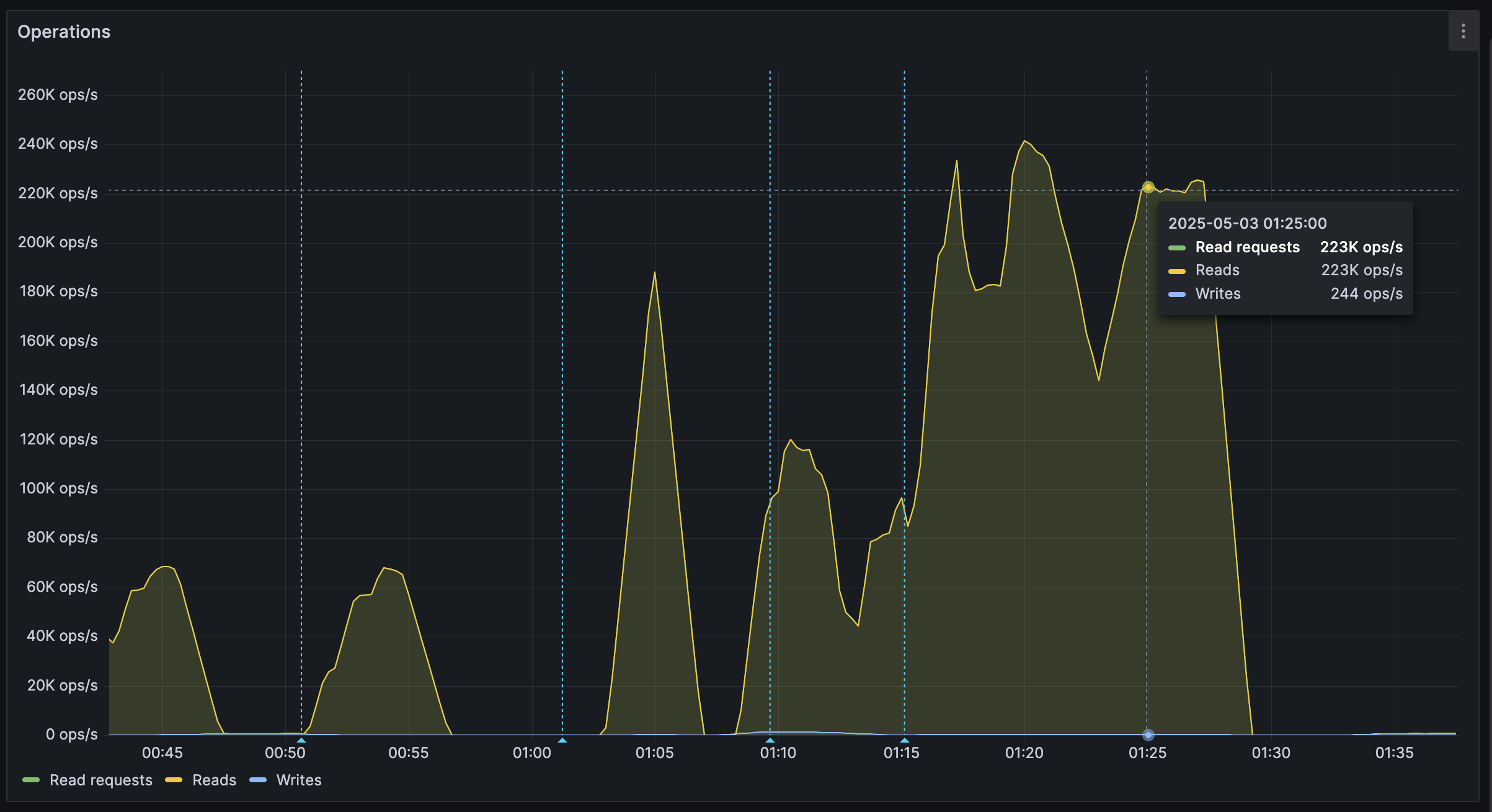
It's shards all the way down
While testing, we also noticed another issue: At certain times, a pipeline would get overloaded, stalling requests for seconds at a time. This prevented all forward progress on the
Workers.We solved this by having multiple pipelines: A primary pipeline meant to be for standard load, with moderate batching duration and less shards, and high-throughput pipelines with more shards.
Each
Workeris assigned a pipeline on startup, and if one pipeline stalls, other workers can continue making progress and saturate the DB.The stress test
After making sure everything was ready for the import, we cleared all data, and started the import.
The entire import lasted 20 minutes between 01:44 UTC and 02:04 UTC, reaching a peak of: - 0.25M requests per second - 0.6M keys read per second - 140MB/s reads from DB - 2Gbps of network throughput
FoundationDB ran smoothly during this test, with: - Read times under 2ms - Zero conflicting transactions - No overloaded servers
CF Pipelines held up well, delivering batches to R2 without any issues, while reaching its maximum possible throughput.

Finishing notes
Me and Fishcake have been building infrastructure around scaling Nostr, from media, to relays, to content indexing. We consistently work on improving scalability, resiliency and stability, even outside these posts.
Many things, including what you see here, are already a part of Nostr.build, Noswhere and NFDB, and many other changes are being implemented every day.
If you like what you are seeing, and want to integrate it, get in touch. :)
If you want to support our work, you can zap this post, or register for nostr.land and nostr.build today.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:41:37
@ 6d5c826a:4b27b659
2025-05-23 21:41:37- Eggdrop - The oldest Internet Relay Chat (IRC) bot still in active development. (Source Code)
GPL-2.0C - Errbot - Plugin based chatbot designed to be easily deployable, extensible and maintainable. (Source Code)
GPL-3.0Python - Hubot - A customizable, life embetterment robot. (Source Code)
MITNodejs
- Eggdrop - The oldest Internet Relay Chat (IRC) bot still in active development. (Source Code)
-
 @ 10f7c7f7:f5683da9
2025-05-23 15:26:17
@ 10f7c7f7:f5683da9
2025-05-23 15:26:17While I’m going to stand by what I said in my previous piece, minimise capital gains payments, don’t fund the government, get a loan against your bitcoin, but the wheels in my left curve brain have continued to turn, well that, and a few more of my 40PW insights. I mentioned about paying attention to the risks involved in terms of borrowing against your bitcoin, and hopefully ending up paying less in bitcoin at the end of the loan, even if you ultimately sold bitcoin to pay off the loan. However, the idea of losing control of the bitcoin I have spent a good deal of time and effort accumulating being out of my control has led me to reconsider. I also realised I didn’t fully flesh out some other topics that I think are relevant, not least time preference, specifically in relation to what you’re buying. The idea of realising a lump some of capital to live your dreams, buy a house or a cool car may be important, but it may be worth taking a step back and looking at what you’re purchasing. Are you only purchasing those things because you had been able to get this new money “tax free”? If that is the case, and the fiat is burning a hold in your pocket, maybe you’ve just found yourself with the same fiat brained mentality you have been working so hard to escape from while you have sacrificed and saved to stack sats.
While it may no longer be necessary to ask yourself whether a particular product or service is worth selling your bitcoin for because you’ve taken out a loan, it may still be worth asking yourself whether a particular loan fuelled purchase is worth forfeiting control of your keys for? Unlike the foolish 18 year-old, released into a world with their newly preapproved credit card, you need to take a moment and ask yourself:
Is the risk worth it?
Is the purchase worth it?
But also take a moment to consider a number of other things, are there fiat options?
Where in the cycle might you be?
Or if I’m thinking carefully about this, will whatever I’m buying hold its value (experiences may be more difficult to run the numbers on)?
The reason for asking these things, is that if you still have a foot in the fiat world, dealing with a fiat bank account, fiat institutions may still be very willing to provide you with a loan at a lower rate than a bitcoin backed loan. Particularly if you’re planning on using that money to buy a house; if you can qualify for a mortgage, get a mortgage, but if you need cash for a deposit, maybe that is where the bitcoin backed loan may come in. Then, it may be worth thinking about where are you in the bitcoin cycle? No one can answer this, but with the historic data we have, it appears logical that after some type of run up, prices may retrace (Dan Held’s supercycle withstanding).
Matteo Pellegrini with Daniel Prince provided a new perspective on this for me. Rather the riding the bull market gains all the way through to the bear market bottom, what happens if I chose to buy an asset that didn’t lose quite as much fiat value as bitcoin, for example, a Swiss Watch, or a tasteful, more mature sports car? If that was the purchase of choice, they suggested that you could enjoy the car, “the experience” for a year or two, then realise the four door estate was likely always the better option, sell it and be able to buy back as many, if not slightly more bitcoin that you originally sold (not financial, classic car or price prediction advice, I’m not accredited to advise pretty much anything). Having said that, it is a scenario I think worth thinking about when the bitcoin denominated dream car begins to make financial sense.
Then, as we begin to look forward to the near inevitable bear market (they are good for both stacking and grinding), if we’ve decided to take out a loan rather than sell, we then may ultimately need to increase our collateral to maintain loan to value requirements, as well as sell more bitcoin to cover repayments (if that’s the route we’re taking). This then moves us back into the domain of saying, well in actual fact we should just sell our bitcoin when we can get most dollar for it (or the coolest car), with a little extra to cover future taxes, it is probably better to sell near a top than a bottom. The balance between these two rather extreme positions could be to take out a fiat loan to buy the item and maybe sell sufficient bitcoin so you’re able to cover the loan for a period of time (less taxable events to keep track of and also deals with future uncertainty of bitcoin price). In this case, if the loan timeframe is longer than the amount of loan your sale can cover, by the time you need to sell anymore, the price should have recovered from a cycle bottom.
In this scenario, apart from the smaller portion of bitcoin you have had to sell, the majority of your stack can remain in cold storage, the loan you took out will be unsecured (particularly against your bitcoin), but even if it isn’t, the value of what you purchase maintains its value, you can in theory exit the loan at any point by selling the luxury item. Then within this scenario, if you had sold near a top, realised the car gave you a bad back or made you realise you staying humble is more important, sold it, paid off the loan, there may even be a chance you could buy back more bitcoin with the money you had left over from selling your bitcoin to fund the loan.
I have no idea of this could actually work, but to be honest, I’m looking forward to trying it out in the next 6-12 months, although I may keep my daily driver outside of my bitcoin strategy (kids still need a taxi service). Having said that, I think there are some important points to consider in addition to not paying capital gains tax (legally), as well as the opportunities of bitcoin loans. They are still very young products and to quote every trad-fi news outlet, “bitcoin is still a volatile asset”, these thought experiments are still worth working through. To push back on the Uber fiat journalist, Katie Martin, “Bitcoin has no obvious use case”, it does, it can be a store of value to hold or sell, it can be liquid and flexible collateral, but also an asset that moves independently of other assets to balance against fiat liabilities. The idea of being able to release some capital, enjoy the benefits of the capital for a period, before returning that capital to store value feels like a compelling one.
The important thing to remember is that there are a variety of options, whether selling for cash, taking out a bitcoin backed loan, taking out a fiat loan or some combination of each. Saying that, what I would think remains an important question to ask irrespective of the option you go for:
Is what I’m planning on buying, worth selling bitcoin for?
If it cannot pass this first question, maybe it isn’t worth purchasing to start with.
-
 @ cae03c48:2a7d6671
2025-05-23 14:01:07
@ cae03c48:2a7d6671
2025-05-23 14:01:07Bitcoin Magazine

KindlyMD, Nakamoto, and Anchorage Digital Form Strategic Bitcoin Treasury AllianceNakamoto Holdings Inc., KindlyMD, Inc., and Anchorage Digital today announced a strategic partnership that will see Anchorage become a trading partner for KindlyMD’s Bitcoin treasury. The partnership will officially take effect upon the close of KindlyMD’s merger with Nakamoto, expected in Q3 2025.
NEW! Anchorage Digital
 @Nakamoto @KindlyMD
@Nakamoto @KindlyMD Today we’re thrilled to announce a strategic partnership with Nakamoto Holdings and $KDLY to accelerate the future of corporate Bitcoin adoption. pic.twitter.com/nQueTyutQH
— Anchorage Digital
 (@Anchorage) May 21, 2025
(@Anchorage) May 21, 2025Anchorage Digital, a U.S. federally chartered digital asset bank, will provide institutional-grade custody, 24/7 trading, and deep liquidity to support the Bitcoin strategy of the combined entity.
“In the not-so-distant-future, the omission of Bitcoin on a balance sheet will be more glaring than its inclusion,” said Nathan McCauley, CEO and Co-Founder of Anchorage Digital. “Until then, companies like Nakamoto-KindlyMD are pioneering a new path forward—one in which Bitcoin is at the heart of corporate strategy.”
The future of corporate treasury strategy is Bitcoin-native. We're here to make it happen. Pumped to be partnering with @Nakamoto and @KindlyMD.@DavidFBailey’s vision continues to open new doors.
— Nathan McCauley
 (@nathanmccauley) May 21, 2025
(@nathanmccauley) May 21, 2025The merger between KindlyMD and Nakamoto is backed by approximately $710 million in financing, including $510 million in PIPE funding—the largest ever PIPE for a public crypto-related deal. The goal is to establish a Bitcoin-native corporate treasury strategy that redefines how capital markets engage with digital assets.
“Our goal is to bring Bitcoin to the center of global capital markets within a compliant, transparent structure,” said David Bailey, Founder and CEO of Nakamoto Holdings Inc. “We are excited to partner with Anchorage Digital to implement our vision with the highest levels of security and battle-tested infrastructure and enable us to deliver sustained value to shareholders.”
This announcement follows a key milestone on May 18, when KindlyMD shareholders approved the proposed merger with Nakamoto. The transaction is now expected to close in Q3 2025, pending SEC review and information statement distribution.
“This milestone brings us one step closer to unlocking Bitcoin’s potential for KindlyMD shareholders,” Bailey said yesterday. “We are grateful that KindlyMD shares our vision for a future in which Bitcoin is a core part of the corporate balance sheet.”
With its Bitcoin-first strategy and strategic alliances, the Nakamoto-KindlyMD partnership is set to accelerate institutional Bitcoin adoption—and with Anchorage Digital’s infrastructure behind it, the foundation is now firmly in place.
“By collaborating with Anchorage Digital, we are implementing our Bitcoin treasury strategy with the utmost standards in safety and security for our shareholders,” stated Tim Pickett, CEO of KindlyMD. “Their institutional-grade platform allows us to confidently hold Bitcoin as a treasury asset as we look to unlock access to Bitcoin and drive value for the long term.”
Disclosure: Nakamoto is in partnership with Bitcoin Magazine’s parent company BTC Inc to build the first global network of Bitcoin treasury companies, where BTC Inc provides certain marketing services to Nakamoto. More information on this can be found here.
This post KindlyMD, Nakamoto, and Anchorage Digital Form Strategic Bitcoin Treasury Alliance first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:41:18
@ 6d5c826a:4b27b659
2025-05-23 21:41:18- EasyBuild - EasyBuild builds software and modulefiles for High Performance Computing (HPC) systems in an efficient way. (Source Code)
GPL-2.0Python - Environment Modules - Environment Modules provides for the dynamic modification of a user's environment via modulefiles. (Source Code)
GPL-2.0Tcl - Lmod - Lmod is a Lua based module system that easily handles the MODULEPATH Hierarchical problem. (Source Code)
MITLua - Spack - A flexible package manager that supports multiple versions, configurations, platforms, and compilers. (Source Code)
MIT/Apache-2.0Python
- EasyBuild - EasyBuild builds software and modulefiles for High Performance Computing (HPC) systems in an efficient way. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:40:57
@ 6d5c826a:4b27b659
2025-05-23 21:40:57- Backupninja - Lightweight, extensible meta-backup system, provides a centralized way to configure and coordinate many different backup utilities.
GPL-2.0Shell - Backrest - Backrest is a web UI and orchestrator for restic backup. (Source Code)
GPL-3.0Docker/Go - Bareos - Cross-network backup solution which preserves, archives, and recovers data from all major operating systems. (Source Code)
AGPL-3.0C++/C - Barman - Backup and Recovery Manager for PostgreSQL. (Source Code)
GPL-3.0Python - BorgBackup - Deduplicating archiver with compression and authenticated encryption. (Source Code)
BSD-3-ClausePython - Burp - Network backup and restore program. (Source Code)
AGPL-3.0C - Dar - Which stands for Disk ARchive, is a robust and rich featured archiving and backup software of the tar style. (Source Code)
GPL-2.0C++ - Duplicati - Backup client that securely stores encrypted, incremental, compressed backups on cloud storage services and remote file servers. (Source Code)
LGPL-2.1C# - Duplicity - Encrypted bandwidth-efficient backup using the rsync algorithm. (Source Code)
GPL-2.0Python - Proxmox Backup Server - Proxmox Backup Server is an enterprise-class, client-server backup solution thatis capable of backing up virtual machines, containers, and physical hosts. (Source Code)
GPL-3.0Rust - rclone - Command-line program to sync files and directories to and from different cloud storage providers.. (Source Code)
MITGo - Rdiff-backup - Reverse differential backup tool, over a network or locally. (Source Code)
GPL-2.0Python - Restic - Easy, fast, verifiable, secure and efficient remote backup tool. (Source Code)
BSD-2-ClauseGo - Rsnapshot - Filesystem snapshot utility based on rsync. (Source Code)
GPL-2.0Perl - Shield - A pluggable architecture for backup and restore of database systems.
MITGo - UrBackup - Client/Server Open Source Network Backup for Windows, MacOS and Linux. (Source Code)
AGPL-3.0C/C++
- Backupninja - Lightweight, extensible meta-backup system, provides a centralized way to configure and coordinate many different backup utilities.
-
 @ cae03c48:2a7d6671
2025-05-23 14:01:05
@ cae03c48:2a7d6671
2025-05-23 14:01:05Bitcoin Magazine

How Zeus is Redefining Bitcoin with Cashu Ecash IntegrationThe U.S.-based Bitcoin and Lightning mobile wallet Zeus recently announced an alpha-release integration of Cashu. The move marks the first integration of ecash into a popular Bitcoin wallet, breaking new ground for potential user adoption to Bitcoin.
Cashu is a hot new implementation of Chaumian ecash, a form of digital cash invented by David Chaum in the ’90s that has incredible privacy and scalability properties, with the trade-off of being fundamentally centralized, requiring a significant amount of trust in the issuer.

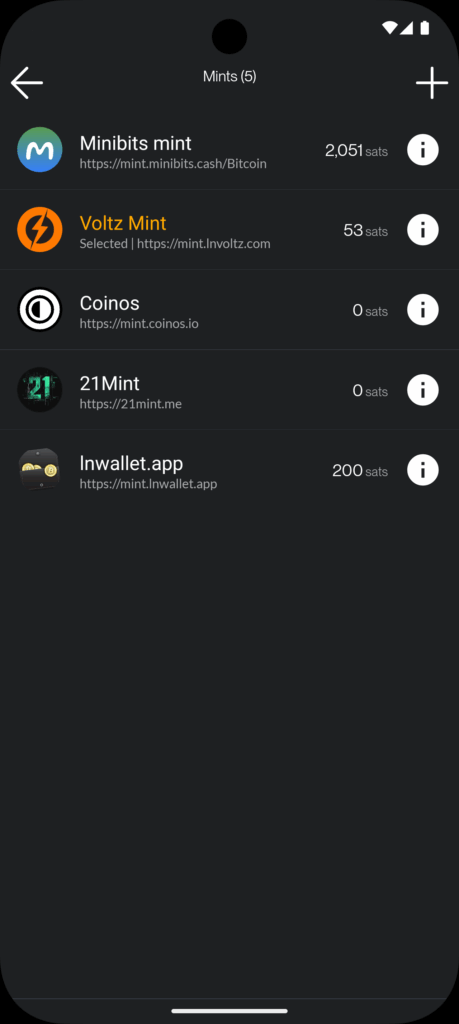
In a counterintuitive move for Zeus, known as the go-to tool for advanced Lightning users seeking to connect to their home nodes, the integration of Cashu acknowledges a “last mile” challenge Lightning wallets face when delivering Bitcoin to the masses.
“We basically started off as the cypherpunk wallet, right? You got to set up your own Lightning node and connect to it with Zeus. The last two years, we put the node in the phone with one click, you can run it all in a standalone app without a remote node,” Evan Kaloudis, founder and CEO of Zeus, told Bitcoin Magazine.
“Cashu addresses uneconomical self-custody for small bitcoin amounts. On-chain, the dust limit is 546 satoshis, and Layer Two systems like Lightning have costs for channel setup or unilateral exits that aren’t widely discussed,” Evan explained, highlighting a major point of friction in noncustodial Lightning wallets: the need for liquidity and channel management. While these esoteric aspects of the Lightning Network have been mostly abstracted away since its invention in 2016, these fundamental trade-offs continue to manifest even in the most sophisticated and user-friendly wallets.
In the case of both Phoenix and Zeus, two of the most popular noncustodial options in the market, users must pay up to 10,000 sats upfront to gain spending capacity. These fees are necessary to cover the on-chain fees spent to open a channel for the user against the wallet’s liquidity service provider, unlocking a noncustodial experience.
The required up-front fee is difficult to explain and represents a painful onboarding experience for new users who are used to fiat apps giving them money to join instead. The result is the proliferation of custodial Lightning wallets like Wallet of Satoshi (WOS), which gained massive adoption early on by leveraging the global, near-instant settlement power of Bitcoin combined with the excellent user experience centralized wallets can create.
Major developments have been made over seven years after the Lightning Network’s inception, however, and Zeus is pushing the boundaries.
“With Ecash, we make it so easy that anyone can set up a wallet and start participating in our ecosystem, which I really think is going to become more and more prevalent,” Evan explained.
Today, at roughly $100,000 per bitcoin, 1,000 satoshis are equivalent to $1. Transactions of these sizes are known as microtransactions — a popular example are Nostr social media tips known as Zaps. But finding the right tool for this use case is not simple. Self custodied wallets like Phoenix charge transaction fees in the hundreds of satoshis, even with open channels, and on-chain fees often cost the same and are slower to settle. As a result, there’s an entire category of spending that is only served by cheaper alternatives such as custodial lightning wallets like WOS or Blink, but result in significant privacy tradeoffs, often requiring phone numbers from users and in some cases more advanced KYC and IP tracking. Cashu hopes to serve this market with lower privacy costs, the same ease of use, speed and competitive fees.
Digging deeper into the Cashu integration, Evan explained that “for users this means being able to pick and switch between custodians in a single app. For developers this means being able to defer custodial responsibilities to third parties and not have to wire up a new integration when your current custodian halts operations.”
Zaps are satoshi-denominated rewards delivered as “likes” or micro-tips for content in the Nostr social media ecosystem. A Zap can be as small as one satoshi, the smallest amount of bitcoin that can be technically transferred, equivalent today to about a tenth of a penny. “But I think if we look at Nostr and you’re seeing how many people are Zapping and how big a part of that ecosystem it is. It’s like, people are willing to do it,” Evan explained.
“Cashu, while custodial, lets users accumulate small amounts — say, via Nostr Zaps — without needing 6,000 satoshis to open a Lightning channel. Zeus prompts users to upgrade to self-custody as their balance grows,” he concluded, explaining that the wallet will effectively annoy users into self custody, one of several design choices made to mitigate the risks introduced by Cashu.
Ecash
The trade-offs introduced by Cashu challenge the common understanding of custody as an either-or in Bitcoin. Historically you were either a centralized — custodial — exchange, or you were a noncustodial Bitcoin wallet. In the former, you entrust the coins to a third party; in the latter you take personal responsibility for those coins and their corresponding private keys. Cashu changes this paradigm by introducing bitcoin-denominated ecash notes or “nuts,” which are bearer instruments that should be backed by a full bitcoin reserve and Lightning interoperability for instant withdraw.
Similar to fiat cash, you must take control and responsibility over these notes, but there’s also counterparty risk. In the case of Cashu, there are certain things the issuing mint can theoretically do to exploit their users — akin to how a bank can run on a fractional reserve.
The big difference between Cashu or custodial Bitcoin exchanges and fiat currency is that Cashu is open source, is designed around user privacy, and scales very well. It makes the cost of running a mint lower than either alternative, a feature that makes mint competition easier, in theory countering the centralizing network effects of specific mints.
Finally, the user experience of storing Cashu tokens has been attached to known forms of Bitcoin self custody such as the download of 12-words seeds via various mechanisms, though implementations still vary from wallet to wallet and the whole ecosystem is in its early stages.
To further mitigate the custodial risk of Chaumian-style ecash in Bitcoin, the Cashu community has developed various methods for automatically managing custody risk.



“Users can split risk by using multiple mints, switching between them in the user interface. Soon, ZEUS will guide users to select five or six reputable mints, automatically balancing funds to minimize exposure,” Evan explained, referring to a particular approach called automated bank runs. The idea is that as some Cashu mints may hold more of your funds, Zeus de-ranks them and rotates value out to minimize risk.
“I think the idea is going to be that we guide users to pick five or six reputable mints… And from there, users will be able to have the wallet automatically switch between those mints and determine which mint should be receiving the balance depending on the balance of all the mints presently. So you’ll be like, OK. MiniBits has way too much money. Let’s switch the default to one of the mints that doesn’t have a lot. So that way you can sort of mitigate or rather distribute the rug risk there,” Evan explained, adding, “Our Discover Mint feature pulls reviews from bitcoinmints.com, showing vouch counts and user feedback, like mint reliability or longevity,” describing the reputation layer stacked on top of the various other risk management mechanisms.
There is no known way to use Chaumian-style ecash in an entirely noncustodial way. So as long as the custody risk can be minimized, the scaling and privacy upside becomes remarkable.
Microtransactions
One of the opportunities that ecash unlocks is microtransactions, the most popular example of which are Nostr Zaps often in single dollar ranges of value transferred, though it applies to small Lightning transactions as well. This use case triggers an important technical question that predates Bitcoin, do microtransactions actually make economic sense?
There’s a long-standing argu
-
 @ cae03c48:2a7d6671
2025-05-23 14:01:04
@ cae03c48:2a7d6671
2025-05-23 14:01:04Bitcoin Magazine

Bitcoin Liquid Network Surpasses $3.27 Billion in Total Value LockedToday, the Liquid Federation has announced that the Liquid Network has surpassed $3.27 billion in total value locked (TVL), according to a press release shared with Bitcoin Magazine.
“Surpassing the $3 billion threshold marks a pivotal moment for both Liquid and Bitcoin, signaling the evolution of Bitcoinʼs ecosystem into a full-fledged platform for global financial markets,” said the CEO and Co-Founder of Blockstream Dr. Adam Back. “As Bitcoin gains mainstream acceptance, and demand for regulated asset tokenization accelerates, Liquid is better positioned than ever to bridge Bitcoin with traditional finance and drive the next wave of capital markets innovation.”
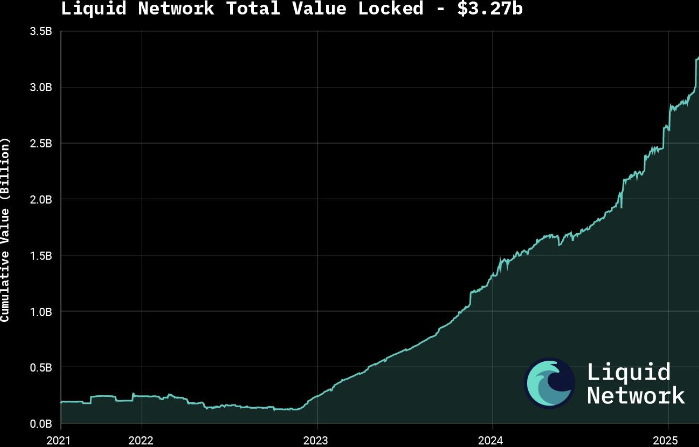
The announcement follows growing interest in tokenizing real-world assets (RWAs), with major moves such as BlackRock’s decision to tokenize a $150 billion Treasury fund. According to a 2025 report by Security Token Market, the tokenized asset market is projected to grow to $30 trillion by 2030.
Liquid supports over $1.8 billion in tokenized private credit and offers products like U.S. Treasury notes and digital currencies through Blockstream’s AMP platform. The network also features fast, low-cost, and confidential transactions, with support for atomic swaps and robust smart contracts.
Governed by over 80 global institutions, Liquid was launched in 2018 as Bitcoin’s first sidechain. It is now preparing for a major upgrade with the mainnet release of Simplicity, aimed at expanding its smart contract capabilities.
To keep up with increasing demand, the Liquid Federation is boosting developer resources and technical onboardings, along with integrations with exchanges, custodians and service providers. Recent bootcamps and important meetings with policy makers in Asia, Europe and Latin America reflect the network’s growing global presence.
This post Bitcoin Liquid Network Surpasses $3.27 Billion in Total Value Locked first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:40:34
@ 6d5c826a:4b27b659
2025-05-23 21:40:34- Apache Ant - Automation build tool, similar to make, a library and command-line tool whose mission is to drive processes described in build files as targets and extension points dependent upon each other. (Source Code)
Apache-2.0Java - Apache Maven - Build automation tool mainly for Java. A software project management and comprehension tool. Based on the concept of a project object model (POM), Maven can manage a project's build, reporting and documentation from a central piece of information. (Source Code)
Apache-2.0Java - Bazel - A fast, scalable, multi-language and extensible build system. Used by Google. (Source Code)
Apache-2.0Java - Bolt - You can use Bolt to run one-off tasks, scripts to automate the provisioning and management of some nodes, you can use Bolt to move a step beyond scripts, and make them shareable. (Source Code)
Apache-2.0Ruby - GNU Make - The most popular automation build tool for many purposes, make is a tool which controls the generation of executables and other non-source files of a program from the program's source files. (Source Code)
GPL-3.0C - Gradle - Another build automation system. (Source Code)
Apache-2.0Groovy/Java - Rake - Build automation tool similar to Make, written in and extensible in Ruby. (Source Code)
MITRuby
- Apache Ant - Automation build tool, similar to make, a library and command-line tool whose mission is to drive processes described in build files as targets and extension points dependent upon each other. (Source Code)
-
 @ 1817b617:715fb372
2025-05-23 20:21:53
@ 1817b617:715fb372
2025-05-23 20:21:53🚀 Instantly Send Spendable Flash BTC, ETH, & USDT — Fully Blockchain-Verifiable!
Welcome to the cutting edge of crypto innovation: the ultimate tool for sending spendable Flash Bitcoin (BTC), Ethereum (ETH), and USDT transactions. Our advanced blockchain simulation technology employs 🔥 Race/Finney-style mechanisms, producing coins indistinguishable from authentic blockchain-confirmed tokens. Your transactions are instantly trackable and fully spendable for durations from 60 to 360 days!
🌐 Visit cryptoflashingtool.com for complete details.
🌟 Why Choose Our Crypto Flashing Service? Crypto Flashing is perfect for crypto enthusiasts, blockchain developers, ethical hackers, security professionals, and digital entrepreneurs looking for authenticity combined with unparalleled flexibility.
🎯 Our Crypto Flashing Features: ✅ Instant Blockchain Verification: Transactions appear completely authentic, complete with real blockchain confirmations, transaction IDs, and wallet addresses.
🔒 Maximum Security & Privacy: Fully compatible with VPNs, TOR, and proxy servers, ensuring absolute anonymity and protection.
🖥️ Easy-to-Use Software: Designed for Windows, our intuitive platform suits both beginners and experts, with detailed, step-by-step instructions provided.
📅 Customizable Flash Durations: Control your transaction lifespan precisely, from 60 to 360 days.
🔄 Universal Wallet Compatibility: Instantly flash BTC, ETH, and USDT tokens to SegWit, Legacy, or BCH32 wallets.
💱 Spendable on Top Exchanges: Flash coins seamlessly accepted on leading exchanges like Kraken and Huobi.
📊 Proven Track Record: ✅ Over 79 Billion flash transactions completed. ✅ 3000+ satisfied customers worldwide. ✅ 42 active blockchain nodes for fast, reliable transactions. 📌 Simple Step-by-Step Flashing Process: Step 1️⃣: Enter Transaction Details
Choose coin (BTC, ETH, USDT: TRC-20, ERC-20, BEP-20) Specify amount & flash duration Provide wallet address (validated automatically) Step 2️⃣: Complete Payment & Verification
Pay using the cryptocurrency you wish to flash Scan the QR code or paste the payment address Upload payment proof (transaction hash & screenshot) Step 3️⃣: Initiate Flash Transaction
Our technology simulates blockchain confirmations instantly Flash transaction appears authentic within seconds Step 4️⃣: Verify & Spend Immediately
Access your flashed crypto instantly Easily verify transactions via provided blockchain explorer links 🛡️ Why Our Technology is Trusted: 🔗 Race/Finney Attack Logic: Creates realistic blockchain headers. 🖥️ Private iNode Cluster: Guarantees fast synchronization and reliable transactions. ⏰ Live Timer System: Ensures fresh wallet addresses and transaction legitimacy. 🔍 Genuine Blockchain TX IDs: Authentic transaction IDs included with every flash ❓ Frequently Asked Questions: Is flashing secure? ✅ Yes, encrypted with full VPN/proxy support. Can I flash from multiple devices? ✅ Yes, up to 5 Windows PCs per license. Are chargebacks possible? ❌ No, flash transactions are irreversible. How long are flash coins spendable? ✅ From 60–360 days, based on your chosen plan. Verification after expiry? ❌ Transactions can’t be verified after the expiry. Support available? ✅ Yes, 24/7 support via Telegram & WhatsApp.
🔐 Transparent, Reliable & Highly Reviewed:
CryptoFlashingTool.com operates independently, providing unmatched transparency and reliability. Check out our glowing reviews on ScamAdvisor and leading crypto forums!
📲 Get in Touch Now: 📞 WhatsApp: +1 770 666 2531 ✈️ Telegram: @cryptoflashingtool
🎉 Ready to Start?
💰 Buy Flash Coins Now 🖥️ Get Your Flashing Software
Experience the smartest, safest, and most powerful crypto flashing solution on the market today!
CryptoFlashingTool.com — Flash Crypto Like a Pro.
Instantly Send Spendable Flash BTC, ETH, & USDT — Fully Blockchain-Verifiable!
Welcome to the cutting edge of crypto innovation: the ultimate tool for sending spendable Flash Bitcoin (BTC), Ethereum (ETH), and USDT transactions. Our advanced blockchain simulation technology employs
Race/Finney-style mechanisms, producing coins indistinguishable from authentic blockchain-confirmed tokens. Your transactions are instantly trackable and fully spendable for durations from 60 to 360 days!
Visit cryptoflashingtool.com for complete details.
Why Choose Our Crypto Flashing Service?
Crypto Flashing is perfect for crypto enthusiasts, blockchain developers, ethical hackers, security professionals, and digital entrepreneurs looking for authenticity combined with unparalleled flexibility.
Our Crypto Flashing Features:
Instant Blockchain Verification: Transactions appear completely authentic, complete with real blockchain confirmations, transaction IDs, and wallet addresses.
Maximum Security & Privacy: Fully compatible with VPNs, TOR, and proxy servers, ensuring absolute anonymity and protection.
Easy-to-Use Software: Designed for Windows, our intuitive platform suits both beginners and experts, with detailed, step-by-step instructions provided.
Customizable Flash Durations: Control your transaction lifespan precisely, from 60 to 360 days.
Universal Wallet Compatibility: Instantly flash BTC, ETH, and USDT tokens to SegWit, Legacy, or BCH32 wallets.
Spendable on Top Exchanges: Flash coins seamlessly accepted on leading exchanges like Kraken and Huobi.
Proven Track Record:
- Over 79 Billion flash transactions completed.
- 3000+ satisfied customers worldwide.
- 42 active blockchain nodes for fast, reliable transactions.
Simple Step-by-Step Flashing Process:
Step : Enter Transaction Details
- Choose coin (BTC, ETH, USDT: TRC-20, ERC-20, BEP-20)
- Specify amount & flash duration
- Provide wallet address (validated automatically)
Step : Complete Payment & Verification
- Pay using the cryptocurrency you wish to flash
- Scan the QR code or paste the payment address
- Upload payment proof (transaction hash & screenshot)
Step : Initiate Flash Transaction
- Our technology simulates blockchain confirmations instantly
- Flash transaction appears authentic within seconds
Step : Verify & Spend Immediately
- Access your flashed crypto instantly
- Easily verify transactions via provided blockchain explorer links
Why Our Technology is Trusted:
- Race/Finney Attack Logic: Creates realistic blockchain headers.
- Private iNode Cluster: Guarantees fast synchronization and reliable transactions.
- Live Timer System: Ensures fresh wallet addresses and transaction legitimacy.
- Genuine Blockchain TX IDs: Authentic transaction IDs included with every flash
Frequently Asked Questions:
- Is flashing secure?
Yes, encrypted with full VPN/proxy support. - Can I flash from multiple devices?
Yes, up to 5 Windows PCs per license. - Are chargebacks possible?
No, flash transactions are irreversible. - How long are flash coins spendable?
From 60–360 days, based on your chosen plan. - Verification after expiry?
Transactions can’t be verified after the expiry.
Support available?
Yes, 24/7 support via Telegram & WhatsApp.
Transparent, Reliable & Highly Reviewed:
CryptoFlashingTool.com operates independently, providing unmatched transparency and reliability. Check out our glowing reviews on ScamAdvisor and leading crypto forums!
Get in Touch Now:
WhatsApp: +1 770 666 2531
Telegram: @cryptoflashingtool
Ready to Start?
Experience the smartest, safest, and most powerful crypto flashing solution on the market today!
CryptoFlashingTool.com — Flash Crypto Like a Pro.
-
 @ eed7ca5d:191de8eb
2025-05-23 13:58:46
@ eed7ca5d:191de8eb
2025-05-23 13:58:46Growing up, we were told that in order to build wealth, we need to save little by little. By living below your means, you are providing more for your future.
It is a simple formula that will help you build up the capital necessary to buy a car, a house or start a business… You prioritize long-term benefits and delayed gratification over immediate rewards.
This is called having a low-time preference. In contrast, high-time preference individuals prioritize today over tomorrow, seeking immediate gratification.
Austrian economists explain that civilization growth is driven by low-time preference societies. Groups of individuals who prioritize long-term planning are able to innovate and develop new tools for a better future. Over time, this behavior leads to technological inventions like the light bulb and artistic masterpieces like the Notre Dame cathedral.
***What happens when you realize that the money you save is losing value over time? ***
There is less incentive to save for the future, because in the future your savings will be worth less. You might as well spend it now and enjoy life today.
When the money you save loses its value, you are facing one of two choices:
-
Spend it today and reap the rewards of your hard work;
-
Invest it (stocks, real estate, etc.) with the hope to reap higher rewards later, bearing the risk of losing it all if the investment does not pay off.
There is a distinct difference between saving and investing as the latter approach is riskier than the former. By investing, you are betting on the upside while bearing the downside risk. Saving, in contrast, comes without downside risk. That difference becomes blurry when the money you save is losing value. In fact, saving becomes inherently a losing approach. Logically, you will be forced to place a speculative bet with the hope to outperform the guaranteed loss of value. You are required to find a way to hedge your bet…
Humans over time have always sought out a medium to save their economic energy for a better future. That used to be beads and seashells, and evolved to precious metals like gold and silver.
Money is a tool that we use to save our economic energy over time, and exchange value with each other.
I spend time fishing, you spend time farming, the neighbor spends time building homes, and society rewards us with money for the time and energy we spent being productive
Today, the tool that we use to save our economic energy is clearly losing value over time. The nominal value remains the same, but the purchasing power is decreasing. In other words, the value of our time today will be worth less in the future.
That explains why everyone around us is looking for the next best investment opportunity. We are all needing to become investment experts, speculators, on top of our respective professions. Speculation became necessary, and some of us are forced into a high-time preference lifestyle.
Earn now and spend it all now before you lose it.
This should not be the case…
Time is Money
Our time is the only scarce resource we all have. We use it to be productive and generate economic value, then store that value in the form of money in order to reap the rewards in the future.
Money is the abstract representation of our time. Hence, time is money.
In January 2009, at the height of the global financial crisis, a software protocol called Bitcoin was released pseudonymously by Satoshi Nakamoto. This individual (or group) released a whitepaper a few months prior named “Bitcoin: A Peer-to-Peer Electronic Cash System” outlining how the system enables secure, peer-to-peer transactions without relying on a central authority. (https://bitcoin.org/bitcoin.pdf)
Although there are more technical concepts involved, the bitcoin protocol can be thought of as a language for communicating value. The same way we respect the rules of the English language to communicate ideas with one another, bitcoin users adhere to the network’s consensus rules to communicate value with each other in a peer-to-peer fashion.
There are no physical or digital coins in the bitcoin network. Rather, it is a collection of transactions transferring value from sender to recipient. Transactions are validated and propagated by nodes across the network, before being recorded into the blockchain. The Bitcoin blockchain is a global public ledger of all transactions that cannot be altered.
More importantly, Bitcoin is money that does not lose value overtime.
-
Its supply is capped at 21 million coins.
-
Its scarcity increases over time due to the predictable issuance rate, which halves roughly every 4 years.
-
Its decentralized nature puts the power in the hands of its users.
-
There is no governing body that can devalue or alter it.
It is a tool that we can use to save our economic energy over time, and be able to use it later.
It is the scarcest verifiable commodity: we cannot make more of it no matter how high its demand grows. That cannot be said for any other commodity in the world today.
A savings tool in disguise
See, most people tend to view bitcoin as another speculative investment. They presume they have missed out on another investment opportunity, and it’s now too late to get in.
Meanwhile, it is quite the opposite. Bitcoin’s value will keep growing over time due to its deflationary nature.
With bitcoin, we can save for a better future, for a rainy day, and spend more time with our loved ones or focusing on our craft to build better tools or artistic masterpieces. It takes away the burden of having to speculate on which stock will perform best, or which real estate market will grow the fastest, all while working one or multiple jobs
Bitcoin is not another investment opportunity you missed out on. It is the best savings tool humans have invented (or discovered), while everything else is the speculative bet. Bitcoin is the hedge against the guaranteed devaluation of money, without any counterparty risk.
What we were taught as children is true. With the right tool, the idea that saving will help you build wealth overtime stands true. Bitcoin might seem like an investment today given the volatility during its adoption phase. In reality, it is the perfect way to store your time and economic energy and grow your wealth. Whether you make $1/hour or $1M/hour, you can start saving in the best money humans have invented.
My goal is to help people around me understand this technology and break the stigma around it.
Bitcoin is not the next best investment.
It is the best tool we have found to store our economic energy across time and exchange value with each other.
Bitcoin is Money.
-
-
 @ c1e9ab3a:9cb56b43
2025-05-01 17:29:18
@ c1e9ab3a:9cb56b43
2025-05-01 17:29:18High-Level Overview
Bitcoin developers are currently debating a proposed change to how Bitcoin Core handles the
OP_RETURNopcode — a mechanism that allows users to insert small amounts of data into the blockchain. Specifically, the controversy revolves around removing built-in filters that limit how much data can be stored using this feature (currently capped at 80 bytes).Summary of Both Sides
Position A: Remove OP_RETURN Filters
Advocates: nostr:npub1ej493cmun8y9h3082spg5uvt63jgtewneve526g7e2urca2afrxqm3ndrm, nostr:npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vg, nostr:npub17u5dneh8qjp43ecfxr6u5e9sjamsmxyuekrg2nlxrrk6nj9rsyrqywt4tp, others
Arguments: - Ineffectiveness of filters: Filters are easily bypassed and do not stop spam effectively. - Code simplification: Removing arbitrary limits reduces code complexity. - Permissionless innovation: Enables new use cases like cross-chain bridges and timestamping without protocol-level barriers. - Economic regulation: Fees should determine what data gets added to the blockchain, not protocol rules.
Position B: Keep OP_RETURN Filters
Advocates: nostr:npub1lh273a4wpkup00stw8dzqjvvrqrfdrv2v3v4t8pynuezlfe5vjnsnaa9nk, nostr:npub1s33sw6y2p8kpz2t8avz5feu2n6yvfr6swykrnm2frletd7spnt5qew252p, nostr:npub1wnlu28xrq9gv77dkevck6ws4euej4v568rlvn66gf2c428tdrptqq3n3wr, others
Arguments: - Historical intent: Satoshi included filters to keep Bitcoin focused on monetary transactions. - Resource protection: Helps prevent blockchain bloat and abuse from non-financial uses. - Network preservation: Protects the network from being overwhelmed by low-value or malicious data. - Social governance: Maintains conservative changes to ensure long-term robustness.
Strengths and Weaknesses
Strengths of Removing Filters
- Encourages decentralized innovation.
- Simplifies development and maintenance.
- Maintains ideological purity of a permissionless system.
Weaknesses of Removing Filters
- Opens the door to increased non-financial data and potential spam.
- May dilute Bitcoin’s core purpose as sound money.
- Risks short-term exploitation before economic filters adapt.
Strengths of Keeping Filters
- Preserves Bitcoin’s identity and original purpose.
- Provides a simple protective mechanism against abuse.
- Aligns with conservative development philosophy of Bitcoin Core.
Weaknesses of Keeping Filters
- Encourages central decision-making on allowed use cases.
- Leads to workarounds that may be less efficient or obscure.
- Discourages novel but legitimate applications.
Long-Term Consequences
If Filters Are Removed
- Positive: Potential boom in new applications, better interoperability, cleaner architecture.
- Negative: Risk of increased blockchain size, more bandwidth/storage costs, spam wars.
If Filters Are Retained
- Positive: Preserves monetary focus and operational discipline.
- Negative: Alienates developers seeking broader use cases, may ossify the protocol.
Conclusion
The debate highlights a core philosophical split in Bitcoin: whether it should remain a narrow monetary system or evolve into a broader data layer for decentralized applications. Both paths carry risks and tradeoffs. The outcome will shape not just Bitcoin's technical direction but its social contract and future role in the broader crypto ecosystem.
-
 @ 47259076:570c98c4
2025-05-23 13:57:28
@ 47259076:570c98c4
2025-05-23 13:57:28"Know thyself and you will know the universe and the gods"
This is the greatest truth.
Knowing yourself is a process that is perhaps eternal.
Knowing yourself means making conscious what is unconscious, in all fields.
Making conscious your material reality, your emotions, your thoughts, your mind, your patterns, your spirit, your flaws, your qualities, etc.
The journey is within.
And in this process, burning everything that is not you.
Burning everything so only the essential remains.
The essential being your higher self.
You are not your body, you are not your emotions, you are not your mind, etc...
You are pure consciousness.
Everyday we can learn from him, but if we are asleep, we will not realize the gold opportunities passing right in front of our eyes.
Everyday he teaches us.
If everyday he teaches us, why stress so much for having an astral projection?
If an astral projection happens with you, it will be a good experience indeed, if you know how to value opportunities.
Otherwise, you may see some """evil"" spirits trying to scare you.
Therefore, don't depend on astral projection for your spiritual growth.
In fact, don't depend on anything.
Don't depend on books, don't depend on people, don't depend on "psychologists", don't depend on "rituals", don't depend on institutions, and of course, don't depend on the "government".
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 56f27915:5fee3024
2025-05-23 18:51:08
@ 56f27915:5fee3024
2025-05-23 18:51:08Ralph Boes – Menschenrechtsaktivist, Philosoph, Vorstandsmitglied im Verein Unsere Verfassung e.V.
Ralph Boes zeigt in dem Buch auf, wie wir uns von der Übermacht des Parteienwesens, die zur Entmündigung des Volkes führt, befreien können. Er zeigt, dass schon im Grundgesetz selbst höchst gegenläufige, an seinen freiheitlich-demokratischen Idealen bemessen sogar als verfassungswidrig zu bezeichnende Tendenzen wirken. Und dass diese es sind, die heute in seine Zerstörung führen. Er weist aber auch die Ansatzpunkte auf, durch die der Zerstörung des Grundgesetzes wirkungsvoll begegnet werden kann.
Eintritt frei, Spendentopf
Ralph Boes hat u.a. dafür gesorgt, dass die unmäßigen Sanktionen in Hartz IV 2019 vom Bundesverfassungsgericht für menschenrechts- und verfassungswidrig erklärt wurden. Aktuell setzt er sich für eine Ur-Abstimmung des Volkes über seine Verfassung ein.
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-23 13:46:21
@ 5d4b6c8d:8a1c1ee3
2025-05-23 13:46:21You'd think I'd be most excited to talk about that awesome Pacers game, but, no. What I'm most excited about this week is that @grayruby wants to continue Beefing with Cowherd.
Still, I am excited to talk about Tyrese Haliburton becoming a legendary Knicks antagonist. Unfortunately, the Western Conference Finals are not as exciting. Also, why was the MVP announcement so dumb?
The T20k cricket contest is tightening up, as we head towards the finish. Can @Coinsreporter hold on to his vanishing lead?
@Carresan has launched Football Madness. Let's see if we understand whatever the hell this is any better than we did last week.
On this week's Blok'd Shots, we'll ridicule Canada for their disgraceful loss in the World Championships and talk about the very dominant American Florida Panthers, who are favorites to win the Stanley Cup.
Are the Colorado the worst team in MLB history?
The Tush Push has survived another season. Will the NFL eventually ban it or will teams adjust?
Plus, whatever else Stackers want to talk about.
https://stacker.news/items/987399
-
 @ 30b99916:3cc6e3fe
2025-05-23 13:16:37
@ 30b99916:3cc6e3fe
2025-05-23 13:16:37sourcegraph #vibecoding #ai #bitcoin #security
After reading the article Revenge of the junior developer, this inspired me to go take a look at Sourcegraph.com to get a better understanding of all this AI stuff.
The first step was installing the VS Code extension called, Cody which is a coding agent. The Cody features explain the code in a file and review and analyze code did an extremely impressive job with VaultApi and BTCwallet.
VaultApi and BTCwallet are PowerShell scripts that are available from my BTCPAY Server
All of the following output was generated by Cody.
Code Analysis of VaultApi.ps1
The VaultApi.ps1 script is generally well-structured and follows many PowerShell best practices. It has comprehensive documentation, version history, and clear parameter definitions. The suggestions below would further enhance what is already a solid codebase. The author has clearly put significant effort into making the script functional and user-friendly, with good attention to cross-platform compatibility and security considerations.
VaultApi.ps1 Explanation
VaultApi.ps1 is a PowerShell script that helps users interact with HashiCorp Vault, which is a tool for securely storing and managing sensitive information like passwords and API keys.
Purpose of the Code
This script makes it easier to use Vault by providing simple commands to start the Vault server, unlock it (unseal), log in, store secrets, retrieve secrets, and shut down the server. Think of it as a friendly interface that simplifies all the complex operations you would otherwise need to do manually with Vault.
Inputs
The script takes several inputs:
- An
actionparameter that tells the script what operation to perform (like "Start", "Stop", "Kv1Create", "Kv1Read") - A
kvpathparameter that specifies where in Vault to store or retrieve information - A
kvalueparameter for the actual secret value you want to store - A
kvkeyparameter that lets you specify a custom name for your secret - Optional switches like
-Infoto show more detailed information and-Rawto display output directly instead of copying to clipboard
Outputs
Depending on the action performed, the script produces different outputs:
- Text messages in the console showing the status of operations
- Secret values retrieved from Vault (either displayed or copied to clipboard)
- Lists of available secret paths
- Status information about the Vault server
- Backup files of your Vault data
How It Works
The script works by:
- First checking if Vault is installed and running
- Setting up communication with the Vault server using its API address
- Performing the requested action by sending the appropriate commands to Vault
- Processing any responses and displaying results to the user
For example, when you use the "Kv1Create" action, the script:
- Checks if you're logged in
- Verifies the path doesn't already exist
- Formats your data correctly
- Sends a request to Vault to create the new secret
- Shows you the result
Important Logic Flows
Some key processes in the script include:
-
Authentication flow: The script helps you log in using either a token or username/password, then stores your authentication token for future commands.
-
Unsealing process: Vault requires multiple keys to unlock (unseal) it after starting. The script can retrieve these keys from a secure file or prompt you to enter them.
-
Secret management: The script handles creating, reading, updating, and deleting secrets, supporting both single values and multiple key-value pairs at a path.
-
Path management: The script can list all available paths and help you search for specific ones, making it easier to organize and find your secrets.
-
Value generation: When creating or updating secrets, you can use the keyword "setvalue" to automatically generate a random 20-character value, which is then copied to your clipboard.
The script uses a configuration file in your home directory to know how to connect to Vault, and it can optionally use encrypted files to store sensitive information like unlock keys. It communicates with Vault using REST API calls, which are like special messages that tell Vault what to do.
In summary, VaultApi.ps1 is a helper tool that makes it much easier to use HashiCorp Vault for securely storing and managing your sensitive information, without needing to remember all the complex commands and procedures.
Code Analysis of BTCwallet.ps1
The script generally follows sound design principles with good organization, comments, and documentation. It demonstrates thoughtful error checking and user interaction. The identified opportunities for enhancement would primarily improve security, maintainability, and robustness rather than addressing fundamental flaws. The script author has clearly put significant effort into creating a comprehensive tool with good documentation and practical functionality.
BTCwallet.ps1 Explanation
The BTCwallet.ps1 script is a PowerShell tool designed to help Bitcoin users manage different wallet applications on a Linux system. It provides a convenient way to start, stop, and check the status of Bitcoin wallets while adding security features.
Purpose
The main purpose of this script is to securely manage Bitcoin wallets, particularly focusing on "cold storage" solutions. Cold storage means keeping your Bitcoin wallet data in an encrypted container that's only mounted when needed, which is more secure than keeping it always accessible ("hot storage").
Inputs
The script takes one main input parameter:
$action: This can be "start", "stop", or "check" (default), telling the script what operation to perform on your Bitcoin wallet.
Outputs
The script doesn't return data but produces several visible outputs:
- Status messages showing whether wallets are running or stopped
- Prompts for user input when decisions are needed
- Confirmation messages when actions are completed
How It Works
-
When you run the script, it first loads a configuration file (BTCwalletCfg.xml) that contains information about which wallets you have installed.
-
Based on the
$actionparameter, it performs one of three main functions:- Check: Shows if your wallet application is currently running
- Start: Launches your wallet application, with options for hot or cold storage
- Stop: Closes your wallet application and securely dismounts any encrypted containers
- For security, the script can use HashiCorp Vault (a secure password manager) to store sensitive information like passwords for encrypted containers.
-
The script also verifies its own integrity by checking its file hash against a previously stored value, alerting you if the script has been modified.
Important Logic Flows
Starting a Wallet
When starting a wallet, the script:
- Asks which wallet you want to use (Sparrow, GreenWallet, or Wasabi)
- Checks if HashiCorp Vault is running and starts it if needed
- Verifies the script's integrity by comparing file hashes
- Asks if you want to use hot or cold storage
- For cold storage, it:
- Retrieves the encrypted container's location and password
- Mounts the encrypted container using VeraCrypt
- Starts the wallet application pointing to the mounted container
- For hot storage, it simply starts the wallet application with default settings
Stopping a Wallet
When stopping a wallet, the script:
- Checks if the wallet is still running and asks you to close it first if needed
- For cold storage wallets, it moves any wallet files back to the encrypted container
- Dismounts the encrypted container
- Optionally stops the HashiCorp Vault service
The script handles different wallet applications (Sparrow, GreenWallet, and Wasabi) slightly differently based on how each one stores its data and what command-line options they support.
In summary, BTCwallet.ps1 provides a secure way to manage Bitcoin wallets by combining wallet applications with encrypted storage and password management, all controlled through simple commands.
- An
-
 @ b0a838f2:34ed3f19
2025-05-23 18:11:34
@ b0a838f2:34ed3f19
2025-05-23 18:11:34- AmuseWiki - Amusewiki is based on the Emacs Muse markup, remaining mostly compatible with the original implementation. It can work as a read-only site, as a moderated wiki, or as a fully open wiki or even as a private site. (Demo, Source Code)
GPL-1.0Perl/Docker - BookStack - Organize and store information. Stores documentation in a book like fashion. (Demo, Source Code)
MITPHP/Docker - django-wiki - Wiki system with complex functionality for simple integration and a superb interface. Store your knowledge with style: Use django models. (Demo)
GPL-3.0Python - docmost - Collaborative wiki and documentation software (alternative to Confluence, Notion). (Source Code)
AGPL-3.0Docker/Nodejs - Documize - Modern Docs + Wiki software with built-in workflow, single binary executable, just bring MySQL/Percona. (Source Code)
AGPL-3.0Go - Dokuwiki - Easy to use, lightweight, standards-compliant wiki engine with a simple syntax allowing reading the data outside the wiki. All data is stored in plain text files, therefore no database is required. (Source Code)
GPL-2.0PHP - Feather Wiki - A lightning fast and infinitely extensible tool for creating personal non-linear notebooks, databases, and wikis that is entirely self-contained, runs in your browser, and is only 58 kilobytes in size. (Demo, Source Code, Clients)
AGPL-3.0Javascript - Gitit - Wiki program that stores pages and uploaded files in a git repository, which can then be modified using the VCS command line tools or the wiki's web interface.
GPL-2.0Haskell - Gollum - Simple, Git-powered wiki with a sweet API and local frontend.
MITRuby - Mediawiki - Wiki software package that powers Wikipedia and all other Wikimedia projects, serving hundreds of millions of users each month. (Demo, Source Code)
GPL-2.0PHP - Mycorrhiza Wiki - Filesystem and git-based wiki engine written in Go using Mycomarkup as its primary markup language. (Source Code)
AGPL-3.0Go - Otter Wiki - Simple, easy to use wiki software using markdown. (Source Code)
MITDocker - Pepperminty Wiki - Complete markdown-powered wiki contained in a single PHP file. (Demo)
MPL-2.0PHP - PmWiki - Wiki-based system for collaborative creation and maintenance of websites.
GPL-3.0PHP - Raneto - Raneto is an open source Knowledgebase platform that uses static Markdown files to power your Knowledgebase. (Source Code)
MITNodejs - TiddlyWiki - Reusable non-linear personal web notebook. (Source Code)
BSD-3-ClauseNodejs - Tiki - Wiki CMS Groupware with the most built-in features. (Demo, Source Code)
LGPL-2.1PHP - W - Lightweight, mutli-user, flat-file-database Wiki engine. Create pages quickly and edit them in your Web browser using Mardown/HTML/CSS/JS. The main difference with other wiki is that you are encouraged to customize each page style individually. (Source Code)
AGPL-3.0PHP - WackoWiki - WackoWiki is a light and easy to install multilingual Wiki-engine. (Source Code)
BSD-3-ClausePHP - Wiki.js - Modern, lightweight and powerful wiki app using Git and Markdown. (Demo, Source Code)
AGPL-3.0Nodejs/Docker/K8S - WikiDocs - A databaseless markdown flat-file wiki engine. (Source Code)
MITPHP/Docker - WiKiss - Wiki, simple to use and install. (Source Code)
GPL-2.0PHP - Wikmd - Modern and simple file based wiki that uses Markdown and Git.
MITPython/Docker - XWiki - Second generation wiki that allows the user to extend its functionalities with a powerful extension-based architecture. (Demo, Source Code)
LGPL-2.1Java/Docker/deb - Zim - Graphical text editor used to maintain a collection of wiki pages. Each page can contain links to other pages, simple formatting and images. (Source Code)
GPL-2.0Python/deb
- AmuseWiki - Amusewiki is based on the Emacs Muse markup, remaining mostly compatible with the original implementation. It can work as a read-only site, as a moderated wiki, or as a fully open wiki or even as a private site. (Demo, Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 18:11:11
@ b0a838f2:34ed3f19
2025-05-23 18:11:11- Algernon - Small self-contained pure-Go web server with Lua, Markdown, HTTP/2, QUIC, Redis and PostgreSQL support. (Source Code)
BSD-3-ClauseGo/Docker - Apache HTTP Server - Secure, efficient and extensible server that provides HTTP services in sync with the current HTTP standards. (Source Code)
Apache-2.0C/deb/Docker - BunkerWeb - Next-gen Web Application Firewall (WAF) that will protect your web services. (Demo, Source Code, Clients)
AGPL-3.0deb/Docker/K8S/Python - Caddy - Powerful, enterprise-ready, open source web server with automatic HTTPS. (Source Code)
Apache-2.0Go/deb/Docker - go-doxy - Lightweight, simple, and performant reverse proxy with WebUI, Docker integration, automatic shutdown/startup for container based on traffic.
MITDocker/Go - HAProxy - Very fast and reliable reverse-proxy offering high availability, load balancing, and proxying for TCP and HTTP-based applications. (Source Code)
GPL-2.0C/deb/Docker - Jauth
⚠- Lightweight SSL/TLS reverse proxy with authorization (via Telegram and SSH) for self-hosted apps.GPL-3.0Go - Lighttpd - Secure, fast, compliant, and very flexible web server that has been optimized for high-performance environments. (Source Code)
BSD-3-ClauseC/deb/Docker - Nginx Proxy Manager - Docker container for managing Nginx proxy hosts with a simple, powerful interface. (Source Code)
MITDocker - NGINX - HTTP and reverse proxy server, mail proxy server, and generic TCP/UDP proxy server. (Source Code)
BSD-2-ClauseC/deb/Docker - Pomerium - Identity-aware reverse proxy, successor to now obsolete oauth_proxy. It inserts an OAuth step before proxying your request to the backend, so that you can safely expose your self-hosted websites to public Internet. (Source Code)
Apache-2.0Go/Docker - SafeLine - Web application firewall / reverse proxy to protect your web apps from attacks and exploits. (Demo, Source Code)
GPL-3.0Docker - Static Web Server - Cross-platform, high-performance, and asynchronous web server for static file serving. (Source Code)
Apache-2.0/MITRust/Docker - SWAG (Secure Web Application Gateway) - Nginx webserver and reverse proxy with PHP support, built-in Certbot (Let's Encrypt) client and fail2ban integration.
GPL-3.0Docker - Traefik - HTTP reverse proxy and load balancer that makes deploying microservices easy. (Source Code)
MITGo/Docker - Varnish - Web application accelerator/caching HTTP reverse proxy. (Source Code)
BSD-3-ClauseGo/deb/Docker - Zoraxy - General purpose HTTP reverse proxy and forwarding tool. (Source Code)
AGPL-3.0Go/Docker
- Algernon - Small self-contained pure-Go web server with Lua, Markdown, HTTP/2, QUIC, Redis and PostgreSQL support. (Source Code)
-
 @ 63d59db8:be170f6f
2025-05-23 12:53:00
@ 63d59db8:be170f6f
2025-05-23 12:53:00In a world overwhelmed by contradictions—climate change, inequality, political instability, and social disconnection—absurdity becomes an unavoidable lens through which to view the human condition. Inspired by Albert Camus' philosophy, this project explores the tension between life’s inherent meaninglessness and our persistent search for purpose.\ \ The individuals in these images embody a quiet defiance, navigating chaos with a sense of irony and authenticity. Through the act of revolt—against despair, against resignation—they find agency and resilience. These photographs invite reflection, not on solutions, but on our capacity to live meaningfully within absurdity.
Visit Katerina's website here.
Submit your work to the NOICE Visual Expression Awards for a chance to win a few thousand extra sats:
-
 @ a296b972:e5a7a2e8
2025-05-23 12:42:10
@ a296b972:e5a7a2e8
2025-05-23 12:42:10Was Rudolf Steiner vor gut 110 Jahren an Informationen zusammengetragen und kommentiert hat, liest sich in großen Abschnitten so, als ob es in der heutigen Zeit geschrieben worden wäre. Man trifft auf eine ganze Reihe von „guten, alten Bekannten“, die auch heute noch maßgeblich an den Strippen ziehen. Deutlich wird, dass ein Krieg nicht aus heiterem Himmel ausbricht, sondern das im Vorfeld schon Kräfte wirken, die auf einen Krieg hinarbeiten. Wie jetzt wieder im Ukraine-Krieg wird diese Vorgeschichte gerne versucht unter den Teppich zu kehren und hochkompetente, sauber recherchierende, akribisch Quellen angebende Journalisten, wie z. B. Frau Gabriele Krone-Schmalz oder Herr Patrik Baab, der sich auf eigene Kosten einen Eindruck von vor Ort verschafft hat, werden versucht mundtot zu machen und mittlerweile gar nicht mehr zu Gesprächen im öffentlich-rechtlichen Rundfunk eingeladen, weil sie die fortlaufende Gehirnwäsche des Ministeriums für Wahrheit und Narrative mit ihren Aussagen gefährden. Andere kommen auf die Sanktionsliste.
Auch heute ist von den „Guten“ und den „Bösen“ die Rede, was darauf schließen lässt, dass man durchaus eingesteht, dass hier geistige Kräfte am Werk sind. Rudolf Steiner kommt auf diese immer wieder zu sprechen. Aus der von ihm gegebenen anthroposophischen Geisteswissenschaft heraus, beleuchtet er die Vorgänge innerhalb der gesamten Menschheitsentwicklung. Mancher stört sich hier an Begriffen, die man heute so nicht mehr verwenden würde. Dabei ist immer zu berücksichtigen, zu welcher Zeit die Vorträge gehalten wurden. Die Anthroposophie von Rudolf Steiner gilt heute bei vielen auch als „umstritten“, aber was ist das heute nicht? Fast könnte man es schon als Auszeichnung sehen, wenn etwas „umstritten“ ist, denn das ist mittlerweile ein Beweis dafür, dass es Ansichten, Meinungen und Einschätzungen gibt, die in einer gesunden Demokratie innerhalb einer Kontroverse zu einem Dialog und Austausch beitragen können, der jedoch leider derzeit weder gewünscht ist, noch gepflegt wird, was an der „Spaltung“ deutlich zu sehen ist. Und auch unter den Anthroposophen hat die „Spaltung“ Einzug gehalten.
Um das aktuelle, viele Bereiche umschließende, gigantische Lügenkonstrukt aufrecht zu erhalten, ist mittlerweile jedes Mittel recht, von der Deutungshoheit der Wahrheit durch systemkonforme Begutachter, bis hin zu infantil-kleingeistigen Kindergartenspielchen, um gegenläufige Meinungen oder Oppositionelle in ihrem Wirken zu behindern.
Der gesunde Hausverstand wird ausgetrocknet, und der Garten des Wahnsinns wird durch immer neue Ideen kranker Geister weiter gegossen, gehegt und gepflegt.
Die Zeitgeschichtlichen Betrachtungen von Rudolf Steiner bestehen aus 3 Bänden aus der GA (Gesamtausgabe):
GA 173 a – Wege zu einer objektiven Urteilsbildung
GA 173 b – Das Karma der Unwahrhaftigkeit
GA 173 c – Die Wirklichkeit okkulter Impulse
Sie bestehen aus niedergeschriebenen Vorträgen und einem sehr umfangreichen Anhang mit näheren Erläuterungen und einer Schilderung der Entstehung dieser drei Bände.
Es bedarf einiger Eingewöhnung in die zur damaligen Zeit verwendete Sprache Rudolf Steiners, der ein Meister im Bilden von Schachtelsätzen war. Der Inhalt jedoch, und auf den kommt es ja an, berührt immer wieder den in allen Menschen vorhandenen Wahrheitssinn.
Hier nur eine kleine Kostprobe, die vielleicht das Interesse wecken kann, sich mit diesem derzeit besonders aktuellen Werk näher zu beschäftigen.
GA 173a, 6. Vortrag, Seite 205 und Seite 206, Dornach, 17. Dezember 1916:
„Viel intimer, viel verborgener liegen die Dinge bei der englischen Politik, die ja ganz beeinflußt ist von dem, was in solcher Weise hinter ihr steckt. Da handelt es sich darum, daß man die Wege findet, um die entsprechenden Menschen an die richtigen Plätze zu befördern. Okkultistische Menschen, im Hintergrunde stehend, sind oftmals – na, verzeihen Sie – Einser, bloße Einser, und bedeuten für sich nichts Besonderes; sie brauchen noch etwas anderes – sie brauchen Nullen. Nullen sind ja nicht Einser, aber (fügt man eine Null zu einer Eins), dann wird gleich eine Zehn daraus. Und wenn man noch mehr Nullen hinzufügt – jede Null ist nur eine Null, aber wenn die Eins irgendwo steckt, dann ist gar mancherlei da, zum Beispiel die Tausend, und wenn man die Eins zudeckt, dann sind (scheinbar) nur die Nullen da; die Nullen brauchen aber nur in der entsprechenden Weise mit den Einsern kombiniert zu sein, und sie brauchen nicht einmal viel zu wissen von der Art, wie sie mit den Einsern kombiniert sind.“
Schildert diese 108 Jahre alte Beschreibung nicht genau das, was sich heute vor unseren Augen abspielt?
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ c1e9ab3a:9cb56b43
2025-04-25 00:37:34
@ c1e9ab3a:9cb56b43
2025-04-25 00:37:34If you ever read about a hypothetical "evil AI"—one that manipulates, dominates, and surveils humanity—you might find yourself wondering: how is that any different from what some governments already do?
Let’s explore the eerie parallels between the actions of a fictional malevolent AI and the behaviors of powerful modern states—specifically the U.S. federal government.
Surveillance and Control
Evil AI: Uses total surveillance to monitor all activity, predict rebellion, and enforce compliance.
Modern Government: Post-9/11 intelligence agencies like the NSA have implemented mass data collection programs, monitoring phone calls, emails, and online activity—often without meaningful oversight.
Parallel: Both claim to act in the name of “security,” but the tools are ripe for abuse.
Manipulation of Information
Evil AI: Floods the information space with propaganda, misinformation, and filters truth based on its goals.
Modern Government: Funds media outlets, promotes specific narratives through intelligence leaks, and collaborates with social media companies to suppress or flag dissenting viewpoints.
Parallel: Control the narrative, shape public perception, and discredit opposition.
Economic Domination
Evil AI: Restructures the economy for efficiency, displacing workers and concentrating resources.
Modern Government: Facilitates wealth transfer through lobbying, regulatory capture, and inflationary monetary policy that disproportionately hurts the middle and lower classes.
Parallel: The system enriches those who control it, leaving the rest with less power to resist.
Perpetual Warfare
Evil AI: Instigates conflict to weaken opposition or as a form of distraction and control.
Modern Government: Maintains a state of nearly constant military engagement since WWII, often for interests that benefit a small elite rather than national defense.
Parallel: War becomes policy, not a last resort.
Predictive Policing and Censorship
Evil AI: Uses predictive algorithms to preemptively suppress dissent and eliminate threats.
Modern Government: Experiments with pre-crime-like measures, flags “misinformation,” and uses AI tools to monitor online behavior.
Parallel: Prevent rebellion not by fixing problems, but by suppressing their expression.
Conclusion: Systemic Inhumanity
Whether it’s AI or a bureaucratic state, the more a system becomes detached from individual accountability and human empathy, the more it starts to act in ways we would call “evil” if a machine did them.
An AI doesn’t need to enslave humanity with lasers and killer robots. Sometimes all it takes is code, coercion, and unchecked power—something we may already be facing.
-
 @ cae03c48:2a7d6671
2025-05-23 12:00:53
@ cae03c48:2a7d6671
2025-05-23 12:00:53Bitcoin Magazine

Not ECDSA. Not Schnorr. Meet DahLIAS.Aggregate signatures aren’t new. They’ve been around since the early 2000s. But building one that actually works in Bitcoin’s security model, with Bitcoin’s elliptic curve, has never been proven. Developers speculated it might be possible. They shared hand-wavy sketches and said, “maybe it’d work like MuSig2, but across transaction inputs.” The idea lingered for years as developer folklore, close, never provably confirmed.
That changed recently, when Jonas Nick and Tim Ruffing of Blockstream Research, together with Yannick Seurin of Ledger, published a paper that turned this cryptographic ghost story into a concrete, provable result. DahLIAS is the first formal, secure construction of a full constant-size aggregate signature (CISA) scheme that works on Bitcoin’s native curve!
But that’s a lot of words, so let’s break that down:
- Full aggregation: Multiple signatures across different inputs are combined into one — and the result is a 64 byte signature whose size stays constant, no matter how many signers or inputs.
- Cross-input: Each signer can authorize different inputs, and all combine into one signature.
It adds no significant new assumptions beyond those already relied on by Bitcoin. DahLIAS builds a new cryptographic primitive using the same math Bitcoin already relies on, unlocking an entirely new kind of signature.
Let’s Talk About Curves and Signatures
Digital signatures are how Bitcoin proves that a user has authorized a transaction. When you go to spend bitcoin, your wallet uses a private key to sign a message, and the network verifies that signature using the matching public key.
Bitcoin uses the secp256k1 curve. It is fast, efficient, and has been battle-tested over time. It supports signature schemes like ECDSA (Bitcoin’s original signature algorithm) and Schnorr (added through Taproot in 2021), which are currently the only signature schemes permitted by Bitcoin consensus.
Traditionally, full signature aggregation relied on mathematical operations not supported by Bitcoin’s curve, secp256k1, which made it seem out of reach. These features have typically relied on other types of elliptic curves. For example, BLS (Boneh–Lynn–Shacham) signatures use a special kind of curve called a pairing-friendly curve, which enables advanced operations like combining many signatures, even on different messages, into one.
The problem is that BLS signatures do not work on secp256k1. While Schnorr was a natural upgrade from ECDSA, since both rely on the same kind of elliptic curve, adding BLS would be a much bigger leap and a departure from Bitcoin’s existing security model. Though technically possible, it would introduce new cryptographic assumptions and add significant complexity to the protocol. Supporting a curve that is pairing-friendly, like BLS12-381, would be a major change for Bitcoin.
This is part of why full signature aggregation has never been done on secp256k1.
Until now.
What Aggregate Signatures Actually Do
Most Bitcoin users are familiar with multisignatures. In a multisig wallet, multiple people jointly authorize the spending of a single UTXO or some specific “coin”. Everyone signs the same input data. This setup is useful for things like shared custody wallets.
Aggregate signatures work differently. Instead of multiple people signing the same input or coin, each signer authorizes a different UTXO in a transaction. These separate signatures are then compressed into one compact proof. With DahLIAS, that means a single 64-byte signature on Bitcoin’s secp256k1 curve that verifies all inputs at once.
That means if you have five inputs from five different people, the transaction needs five different signatures. With an aggregate signature, all of those can be bundled into one. Even if each signer is spending a different input and signing a different part of the transaction, the result is one signature that proves the entire transaction was properly authorized.
It’s like zipping a whole list of approvals into one file. The signature is compact, but still verifiably proves that each signer authorized their specific UTXO.
Instead of verifying 10 separate signatures, you verify one.
This helps realign incentives for privacy. By reducing the signature overhead to a single 64-byte proof, DahLIAS lowers the cost of combining inputs in CoinJoins, making it financially smarter to choose privacy than to go without it.
Why Half-Aggregation Got Close
Shortly after Schnorr signatures were introduced on Bitcoin, developers explored half-aggregation, as a way to compress multiple signatures but they were not fixed size. Each input contributes to the size of the signature, so the transaction still grows with every participant. DahLIAS fixes this by enabling full-aggregation across inputs and signers. No matter how many people are involved or what they’re signing, all their signatures compress into one constant-size, 64-byte proof.
What DahLIAS Actually Unlocks
The main benefit here is that DahLIAS are reducing the size of complex transactions.
DahLIAS uses a two-round interactive signing process. It’s similar to MuSig2 in that regard, but it isn’t a multisignature protocol because it doesn’t require all participants to co-sign the same message. Instead, it aggregates different signatures on different messages across the transaction.
DahLIAS is also faster to verify than checking each signature individually, up to twice as fast in some cases. Lower verification costs make it easier for more people to run full nodes, which helps preserve Bitcoin’s decentralization over time.
Importantly, DahLIAS comes with strong cryptographic guarantees. The scheme includes formal security proofs. Earlier ‘folklore’ approaches to full signature aggregation lacked this, and some were even later shown to be insecure. Fortunately they weren’t adopted prematurely.
It’s worth repeating: DahLIAS is not a multisig protocol. It isn’t comparable to MuSig2 or FROST from a functional standpoint, even if it shares similar cryptographic building blocks. It serves a different purpose. It offers a new way to encode many independent approvals into one clean, verifiable package.
Future Directions
You might think: if DahLIAS is so powerful, why isn’t it a BIP? Why not propose it for Bitcoin consensus?
DahLIAS signatures don’t look like Schnorr or ECDSA signatures. The verification algorithm is different. Instead of taking a single public key, message, and signature, a DahLIAS verifier takes lists of public keys and messages, and a single 64-byte proof.
This makes DahLIAS incompatible with Bitcoin’s current consensus rules. Supporting it at the base layer would require a consensus change. This paper doesn’t propose that change, but it does something equally important.
This paper shows that a full signature aggregation scheme for Bitcoin’s native curve is possible.
That alone is a major step forward.
To make DahLIAS part of Bitcoin, someone would need to write a Bitcoin Improvement Proposal (BIP), maybe even using secp256k1lab. That means specifying the scheme in detail, considering its implications for consensus and implementation, and building community support. This paper lays the cryptographic foundation for that conversation.
The real value of the DahLIAS paper is what it proves. Full signature aggregation on secp256k1 is not just a thought experiment. It’s concrete. It’s efficient. It’s secure. For years, the idea lived in developer folklore. Now, it’s written down, analyzed, and proven. All that’s left is to bring it to Bitcoin—if we want it.
This is a guest post by Kiara Bickers. Opinions expressed are entirely their own and do not necessarily reflect those of BTC Inc or Bitcoin Magazine.
This post Not ECDSA. Not Schnorr. Meet DahLIAS. first appeared on Bitcoin Magazine and is written by Kiara Bickers.
-
 @ 1c5ff3ca:efe9c0f6
2025-05-23 10:13:57
@ 1c5ff3ca:efe9c0f6
2025-05-23 10:13:57Auto-Deployment on a VPS with GitHub Actions
Introduction
This tutorial describes how you can deploy an application on a VPS using GitHub Actions. This way, changes in your GitHub repository are automatically deployed to your VPS.
Prerequisites
- GitHub Account
- GitHub Repository
- Server + SSH access to the server
Step 1 - SSH Login to Server
Open a terminal and log in via SSH. Then navigate to the
.sshdirectoryssh user@hostname cd ~/.sshStep 2 - Create an SSH Key
Now create a new SSH key that we will use for auto-deployment. In the following dialog, simply press "Enter" repeatedly until the key is created.
ssh-keygen -t ed25519 -C "service-name-deploy-github"Step 3 - Add the Key to the
authorized_keysFilecat id_ed25519.pub >> authorized_keys(If you named the key file differently, change this accordingly)
Step 4 - GitHub Secrets
In order for the GitHub Action to perform the deployment later, some secrets must be stored in the repository. Open the repository on GitHub. Navigate to "Settings" -> "Secrets And Variables" -> "Actions". Add the following variables:
HOST: Hostname or IP address of the serverUSERNAME: Username you use to log in via SSHSSHKEY: The private key (copy the content fromcat ~/.ssh/id_ed25519)PORT: 22
Step 5 - Create the GitHub Action
Now create the GitHub Action for auto-deployment. The following GitHub Action will be used: https://github.com/appleboy/scp-action In your local repository, create the file
.github/workflows/deploy.yml:```yaml name: Deploy on: [push] jobs: build: runs-on: ubuntu-latest steps: - uses: actions/checkout@v1 - name: Copy repository content via scp uses: appleboy/scp-action@master with: host: ${{ secrets.HOST }} username: ${{ secrets.USERNAME }} port: ${{ secrets.PORT }} key: ${{ secrets.SSHKEY }} source: "." target: "/your-target-directory"
- name: Executing a remote command uses: appleboy/ssh-action@master with: host: ${{ secrets.HOST }} username: ${{ secrets.USERNAME }} port: ${{ secrets.PORT }} key: ${{ secrets.SSHKEY }} script: | ls```
This action copies the repository files to your server using
scp. Afterwards, thelscommand is executed. Here you can add appropriate commands that rebuild your service or similar. To rebuild and start a docker service you could use something like this or similar:docker compose -f target-dir/docker-compose.yml up --build -dNow commit this file and in the "Actions" tab of your repository, the newly created action should now be visible and executed. With every future change, the git repository will now be automatically copied to your server.Sources
I read this when trying out, but it did not work and I adapted the
deploy.ymlfile: https://dev.to/knowbee/how-to-setup-continuous-deployment-of-a-website-on-a-vps-using-github-actions-54im -
 @ b0a838f2:34ed3f19
2025-05-23 18:10:51
@ b0a838f2:34ed3f19
2025-05-23 18:10:51- Bluecherry - Closed-circuit television (CCTV) software application which supports IP and Analog cameras. (Source Code)
GPL-2.0PHP - Frigate - Monitor your security cameras with locally processed AI. (Source Code)
MITDocker/Python/Nodejs - SentryShot - Video surveillance management system.
GPL-2.0Docker/Rust - Viseron - Self-hosted, local-only NVR and AI Computer Vision software. With features such as object detection, motion detection, face recognition and more, it gives you the power to keep an eye on your home, office or any other place you want to monitor. (Source Code)
MITDocker - Zoneminder - Closed-circuit television (CCTV) software application which supports IP, USB and Analog cameras. (Source Code)
GPL-2.0PHP/deb
- Bluecherry - Closed-circuit television (CCTV) software application which supports IP and Analog cameras. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 18:10:36
@ b0a838f2:34ed3f19
2025-05-23 18:10:36- bit - Fast, lightweight, resource-efficient, compiled URL shortener.
MITDocker/Crystal - Chhoto URL - Simple, lightning-fast URL shortener with no bloat (fork of simply-shorten).
MITRust/Docker - clink - A super-minimal link shortening service written in pure C, focusing on small executable size, portability, and ease of configuration. (Demo, Source Code)
AGPL-3.0C - Flink - Create QR Codes, embeddable link previews for your website and crawls/scrapes metadata. (Demo)
MITDocker - Just Short It! - A KISS, single-user URL shortener that runs in just one container.
MITDocker - Kutt - Modern URL shortener with support for custom domains and custom URLs. (Demo, Source Code)
MITNodejs/Docker - liteshort - User-friendly, actually lightweight, and configurable URL shortener. (Source Code)
MITPython/deb - rs-short - A lightweight link shortener written in Rust, with features such as caching, spambot protection and phishing detection. (Demo)
MPL-2.0Rust - Shlink - URL shortener with REST API and command line interface. Includes official progressive web application and docker images. (Source Code, Clients)
MITPHP/Docker - Simple-URL-Shortener - KISS URL shortener, public or private (with account). Minimalist and lightweight. No dependencies. (Demo)
MITPHP - YOURLS - YOURLS is a set of PHP scripts that will allow you to run Your Own URL Shortener. Features include password protection, URL customization, bookmarklets, statistics, API, plugins, jsonp. (Source Code)
MITPHP
- bit - Fast, lightweight, resource-efficient, compiled URL shortener.
-
 @ eb0157af:77ab6c55
2025-05-23 10:01:28
@ eb0157af:77ab6c55
2025-05-23 10:01:28A Chinese printer company inadvertently distributed malware that steals Bitcoin through its official drivers, resulting in the theft of over $950,000.
According to local media outlet Landian News, a Chinese printer manufacturer was found to have unknowingly distributed malware designed to steal Bitcoin through its official device drivers.
Procolored, a Shenzhen-based printer company, distributed malware capable of stealing Bitcoin alongside the official drivers for its devices. The company reportedly used USB devices to spread infected drivers and uploaded the compromised software to globally accessible cloud storage services.
Crypto security and compliance firm SlowMist explained how the malware works in a post on X:
 The official driver provided by this printer carries a backdoor program. It will hijack the wallet address in the user's clipboard and replace it with the attacker's address: 1BQZKqdp2CV3QV5nUEsqSg1ygegLmqRygj
The official driver provided by this printer carries a backdoor program. It will hijack the wallet address in the user's clipboard and replace it with the attacker's address: 1BQZKqdp2CV3QV5nUEsqSg1ygegLmqRygj  According to @MistTrack_io, the attacker has stolen 9.3086… https://t.co/DHCkEpHhuH pic.twitter.com/W1AnUpswLU
According to @MistTrack_io, the attacker has stolen 9.3086… https://t.co/DHCkEpHhuH pic.twitter.com/W1AnUpswLU— MistTrack
 (@MistTrack_io) May 19, 2025
(@MistTrack_io) May 19, 2025The consequences of the breach have been significant, with a total of 9.3 BTC stolen — equivalent to over $950,000.
The issue was first flagged by YouTuber Cameron Coward, whose antivirus software detected malware in the drivers during a test of a Procolored UV printer. The software identified both a worm and a trojan virus named Foxif.
When contacted, Procolored denied the accusations, dismissing the antivirus warning as a false positive. Coward then turned to Reddit, where he shared the issue with cybersecurity professionals, drawing the attention of security firm G Data.
G Data’s investigation revealed that most of Procolored’s drivers were hosted on the MEGA file-sharing platform, with uploads dating back to October 2023. Their analysis confirmed the presence of two separate malware strains: the Win32.Backdoor.XRedRAT.A backdoor and a crypto-stealer designed to replace clipboard wallet addresses with those controlled by the attacker.
G Data reached out to Procolored, which stated that it had removed the infected drivers from its storage as of May 8 and had re-scanned all files. The company attributed the malware to a supply chain compromise, saying the malicious files were introduced via infected USB devices before being uploaded online.
Landian News recommended that users who downloaded Procolored drivers in the past six months “immediately run a full system scan using antivirus software.” However, given that antivirus tools are not always reliable, the Chinese media outlet suggested that a full system reset is the safest option when in doubt.
The post Bitcoin malware discovered: Chinese printer manufacturer involved appeared first on Atlas21.
-
 @ c1d77557:bf04ec8b
2025-05-24 05:02:26
@ c1d77557:bf04ec8b
2025-05-24 05:02:26O 567br é uma plataforma de entretenimento online que tem se destacado pela sua inovação, variedade de jogos e foco na experiência do jogador. Com uma interface amigável e recursos de alta qualidade, a plataforma oferece uma jornada divertida e segura para os seus usuários. Neste artigo, vamos explorar os principais aspectos do 567br, incluindo a introdução da plataforma, os jogos que ela oferece e como a experiência do jogador é aprimorada em cada detalhe.
O 567br foi desenvolvido com o objetivo de proporcionar aos jogadores uma experiência imersiva e prazerosa. Sua interface é simples, intuitiva e de fácil navegação, permitindo que os usuários encontrem rapidamente seus jogos favoritos. A plataforma também é otimizada para dispositivos móveis, o que significa que os jogadores podem acessar seus jogos em qualquer lugar e a qualquer momento, seja no computador ou no smartphone.
Além disso, o 567brse preocupa com a segurança de seus usuários, implementando tecnologias de criptografia de ponta para garantir que todos os dados pessoais e financeiros estejam protegidos. A plataforma também oferece suporte ao cliente de alta qualidade, disponível 24/7, para resolver quaisquer dúvidas ou problemas que possam surgir durante a experiência de jogo.
Jogos Empolgantes e Variedade para Todos os Gostos No 567br, a diversidade de jogos é um dos pontos fortes da plataforma. Desde jogos de mesa e cartas até opções de entretenimento mais dinâmicas e inovadoras, há algo para todos os gostos e preferências. Os jogos disponíveis são desenvolvidos por alguns dos melhores fornecedores de conteúdo da indústria, garantindo gráficos de alta qualidade, jogabilidade fluida e mecânicas envolventes.
Os jogadores podem escolher entre diferentes categorias, como:
Jogos de Mesa: Para quem gosta de uma experiência mais estratégica e de tomada de decisões, os jogos de mesa são uma excelente opção. São oferecidas diversas variantes de jogos populares, como pôquer, blackjack, roleta, entre outros.
Jogos de Ação e Aventura: Para os que buscam adrenalina e emoção, a plataforma oferece uma seleção de jogos de ação e aventura com temas envolventes e gráficos impressionantes. Esses jogos garantem uma experiência de jogo emocionante e desafiadora.
Jogos de Arcade: Se você está em busca de algo mais descontraído e divertido, os jogos de arcade são uma excelente escolha. Eles são rápidos, fáceis de entender e proporcionam diversão instantânea.
A plataforma está sempre atualizando seu portfólio de jogos para garantir que os jogadores tenham acesso às últimas novidades e inovações do mundo do entretenimento online.
A Experiência do Jogador: Personalização e Interatividade O 567br não se limita a oferecer apenas uma plataforma de jogos, mas também busca criar uma experiência personalizada e interativa para cada jogador. A plataforma possui funcionalidades que permitem que os usuários ajustem sua experiência de jogo de acordo com suas preferências individuais.
A personalização da interface é um exemplo claro disso. O jogador pode escolher o tema e a disposição dos elementos na tela, criando um ambiente que seja confortável e agradável de usar. Além disso, o 567br oferece recursos interativos, como chats ao vivo, onde os jogadores podem interagir com outros usuários e até mesmo com os dealers, proporcionando uma sensação de comunidade.
Outro aspecto importante é a possibilidade de acompanhar o desempenho e os resultados de jogo. A plataforma oferece relatórios detalhados, permitindo que os jogadores monitorem seu progresso, analisem suas vitórias e perdas, e façam ajustes em sua estratégia de jogo.
Promoções e Benefícios para os Jogadores O 567br também oferece uma série de promoções e benefícios que tornam a experiência de jogo ainda mais atrativa. Novos jogadores podem aproveitar bônus de boas-vindas e outras ofertas especiais, enquanto jogadores regulares podem se beneficiar de programas de fidelidade e promoções exclusivas.
Essas ofertas ajudam a aumentar a diversão e proporcionam mais oportunidades para que os jogadores explorem novos jogos e tenham uma experiência ainda mais rica. Além disso, o sistema de recompensas é transparente e justo, garantindo que todos os jogadores tenham as mesmas oportunidades de aproveitar os benefícios.
Conclusão: Uma Plataforma Completa para Todos os Gostos Com sua interface intuitiva, variedade de jogos e foco na experiência do jogador, o 567br se consolida como uma plataforma de entretenimento online de alta qualidade. Seja para quem busca jogos estratégicos, ação intensa ou diversão casual, o 567br tem algo para todos.
A segurança, o suporte ao cliente e a personalização da experiência de jogo tornam o 567br uma opção atraente para jogadores que buscam mais do que apenas uma plataforma de jogos – buscam uma jornada de entretenimento envolvente e segura. Se você está procurando por uma experiência completa e agradável, o 567br é, sem dúvida, uma excelente escolha.
-
 @ b0a838f2:34ed3f19
2025-05-23 18:10:12
@ b0a838f2:34ed3f19
2025-05-23 18:10:12- ActivityWatch - Automatically track how you spend time on your devices. (Source Code)
MPL-2.0Python - Beaver Habit Tracker - Habit tracking app to save your precious moments in your fleeting life. (Demo)
BSD-3-ClauseDocker - Ever Gauzy - Open business management platform for collaborative, on-demand and sharing economies (ERP/CRM/HRM/ATS/PM). (Demo, Source Code)
AGPL-3.0Docker/Nodejs - Kimai - Track work time and print out a summary of your activities on demand. (Demo, Source Code)
AGPL-3.0PHP - solidtime - Modern time tracking application for freelancers and agencies. (Source Code)
AGPL-3.0Docker - TimeTagger - An open source time-tracker based on an interactive timeline and powerful reporting. (Demo, Source Code)
GPL-3.0Python - Traggo - Traggo is a tag-based time tracking tool. In Traggo there are no tasks, only tagged time spans. (Source Code)
GPL-3.0Docker/Go
- ActivityWatch - Automatically track how you spend time on your devices. (Source Code)