-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:22
@ 04c915da:3dfbecc9
2025-05-20 15:50:22There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
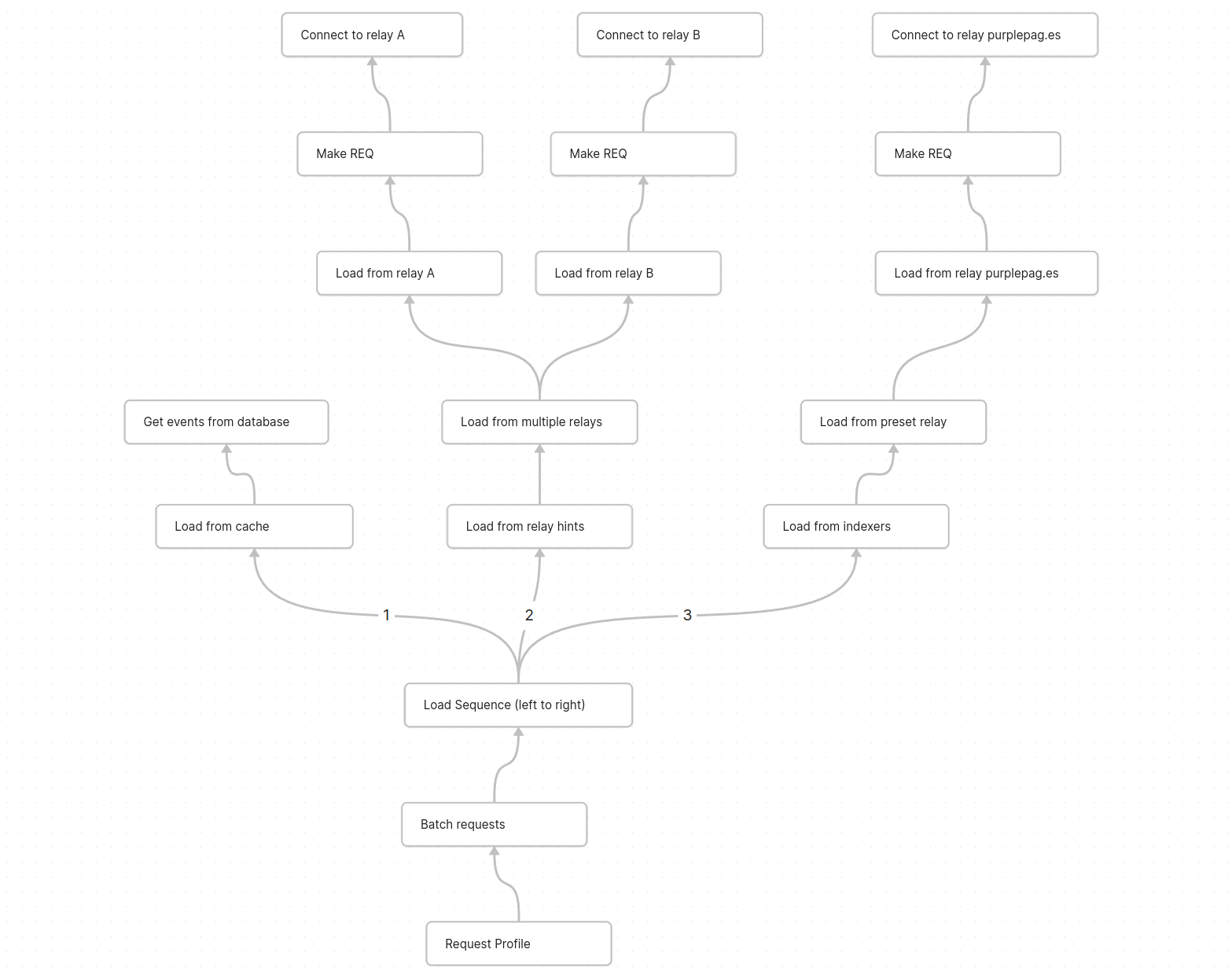
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 611021ea:089a7d0f
2025-05-24 00:00:04
@ 611021ea:089a7d0f
2025-05-24 00:00:04The world of health and fitness data is booming. Users are tracking more aspects of their well-being than ever before, from daily steps and workout intensity to sleep patterns and caloric intake. But for developers looking to build innovative applications on this data, significant hurdles remain: ensuring user privacy, achieving interoperability between different services, and simply managing the complexity of diverse health metrics.
Enter the NIP-101h Health Profile Framework and its companion tools: the HealthNote SDK and the HealthNote API. This ecosystem is designed to empower developers to create next-generation health and fitness applications that are both powerful and privacy-preserving, built on the decentralized and user-centric principles of Nostr.
NIP-101h: A Standardized Language for Health Metrics
At the core of this ecosystem is NIP-101h. It's a Nostr Improvement Proposal that defines a standardized way to represent, store, and share granular health and fitness data. Instead of proprietary data silos, NIP-101h introduces specific Nostr event kinds for individual metrics like weight (kind
1351), height (kind1352), step count (kind1359), and many more.Key features of NIP-101h:
- Granularity: Each piece of health information (e.g., weight, caloric intake) is a distinct Nostr event, allowing for fine-grained control and access.
- User Control: Built on Nostr, the data remains under user control. Users decide what to share, with whom, and on which relays.
- Standardization: Defines common structures for units, timestamps, and metadata, promoting interoperability.
- Extensibility: New metrics can be added as new NIP-101h.X specifications, allowing the framework to evolve.
- Privacy by Design: Encourages the use of NIP-04/NIP-44 for encryption and includes a
consenttag for users to specify data-sharing preferences.
You can explore the full NIP-101h specification and its metric directory in the main project repository.
The HealthNote SDK: Simplifying Client-Side Integration
While NIP-101h provides the "what," the HealthNote SDK provides the "how" for client-side applications. This (currently draft) TypeScript SDK aims to make it trivial for developers to:
- Create & Validate NIP-101h Events: Easily construct well-formed Nostr events for any supported health metric, ensuring they conform to the NIP-101h specification.
- Handle Encryption: Seamlessly integrate with NIP-44 to encrypt sensitive health data before publication.
- Manage Consent: Automatically include appropriate
consenttags (e.g., defaulting toaggregate-only) to respect user preferences. - Publish to Relays: Interact with Nostr relays to publish the user's health data.
- Prepare Data for Analytics: Extract minimal, privacy-preserving "stat-blobs" for use with the HealthNote API.
The SDK's goal is to abstract away the low-level details of Nostr event creation and NIP-101h formatting, letting developers focus on their application's unique features.
The HealthNote API: Powerful Insights, Zero Raw Data Exposure
This is where things get really exciting for developers wanting to build data-driven features. The HealthNote API (detailed in
HealthNote-API.md) is a server-side component designed to provide powerful analytics over aggregated NIP-101h data without ever accessing or exposing individual users' raw, unencrypted metrics.Here's how it achieves this:
- Privacy-Preserving Ingestion: The SDK sends only "stat-blobs" to the API. These blobs contain the numeric value, unit, timestamp, and metric kind, but not the original encrypted content or sensitive user identifiers beyond what's necessary for aggregation.
- Aggregation at its Core: The API's endpoints are designed to return only aggregated data.
GET /trend: Provides time-series data (e.g., average daily step count over the last month).GET /correlate: Computes statistical correlations between two metrics (e.g., does increased activity duration correlate with changes in workout intensity?).GET /distribution: Shows how values for a metric are distributed across the user base.
- Built-in Privacy Techniques:
- k-Anonymity: Ensures that each data point in an aggregated response represents at least 'k' (e.g., 5) distinct users, preventing re-identification.
- Differential Privacy (Optional): Can add statistical noise to query results, further protecting individual data points while preserving overall trends.
- No Raw Data Access for Developers: Developers querying the API receive only these aggregated, anonymized results, perfect for powering charts, dashboards, and trend analysis in their applications.
A Typical Workflow
- A user records a workout in their NIP-101h-compatible fitness app.
- The app uses the HealthNote SDK to create NIP-101h events for metrics like distance, duration, and calories burned. Sensitive data is encrypted.
- The SDK publishes these events to the user's configured Nostr relays.
- The SDK also extracts stat-blobs (e.g.,
{ kind: 1363, value: 5, unit: 'km', ... }) and sends them to the HealthNote API for ingestion, tagged with anaggregate-onlyconsent. - Later, the app (or an authorized third-party service) queries the HealthNote API:
GET /trend?kind=1363&bucket=week&stat=sum. - The API returns a JSON object like:
{"series": [{"date": "2024-W20", "value": 15000}, ...]}showing the total distance run by all consenting users, week by week. This data can directly populate a trend chart.
Benefits for the Ecosystem
- For Users:
- Greater control and ownership of their health data.
- Ability to use a diverse range of interoperable health and fitness apps.
- Confidence that their data can contribute to insights without sacrificing personal privacy.
- For Developers:
- Easier to build sophisticated health and fitness applications without becoming privacy experts or building complex data aggregation pipelines.
- Access to rich, aggregated data for creating compelling user-facing features (trends, benchmarks, correlations).
- Reduced burden of storing and securing sensitive raw health data for analytical purposes.
- Opportunity to participate in an open, interoperable ecosystem.
The Road Ahead
The NIP-101h framework, the HealthNote SDK, and the HealthNote API are foundational pieces for a new generation of health and fitness applications. As these tools mature and gain adoption, we envision a vibrant ecosystem where users can seamlessly move their data between services, and developers can innovate rapidly, all while upholding the highest standards of privacy and user control.
We encourage developers to explore the NIP-101h specifications, experiment with the (upcoming) SDK, and review the HealthNote API design. Your feedback and contributions will be invaluable as we build this privacy-first future for health data.
https://github.com/HealthNoteLabs
-
 @ 3f770d65:7a745b24
2025-05-19 18:09:52
@ 3f770d65:7a745b24
2025-05-19 18:09:52🏌️ Monday, May 26 – Bitcoin Golf Championship & Kickoff Party
Location: Las Vegas, Nevada\ Event: 2nd Annual Bitcoin Golf Championship & Kick Off Party"\ Where: Bali Hai Golf Clubhouse, 5160 S Las Vegas Blvd, Las Vegas, NV 89119\ 🎟️ Get Tickets!
Details:
-
The week tees off in style with the Bitcoin Golf Championship. Swing clubs by day and swing to music by night.
-
Live performances from Nostr-powered acts courtesy of Tunestr, including Ainsley Costello and others.
-
Stop by the Purple Pill Booth hosted by Derek and Tanja, who will be on-boarding golfers and attendees to the decentralized social future with Nostr.
💬 May 27–29 – Bitcoin 2025 Conference at the Las Vegas Convention Center
Location: The Venetian Resort\ Main Attraction for Nostr Fans: The Nostr Lounge\ When: All day, Tuesday through Thursday\ Where: Right outside the Open Source Stage\ 🎟️ Get Tickets!
Come chill at the Nostr Lounge, your home base for all things decentralized social. With seating for \~50, comfy couches, high-tops, and good vibes, it’s the perfect space to meet developers, community leaders, and curious newcomers building the future of censorship-resistant communication.
Bonus: Right across the aisle, you’ll find Shopstr, a decentralized marketplace app built on Nostr. Stop by their booth to explore how peer-to-peer commerce works in a truly open ecosystem.
Daily Highlights at the Lounge:
-
☕️ Hang out casually or sit down for a deeper conversation about the Nostr protocol
-
🔧 1:1 demos from app teams
-
🛍️ Merch available onsite
-
🧠 Impromptu lightning talks
-
🎤 Scheduled Meetups (details below)
🎯 Nostr Lounge Meetups
Wednesday, May 28 @ 1:00 PM
- Damus Meetup: Come meet the team behind Damus, the OG Nostr app for iOS that helped kickstart the social revolution. They'll also be showcasing their new cross-platform app, Notedeck, designed for a more unified Nostr experience across devices. Grab some merch, get a demo, and connect directly with the developers.
Thursday, May 29 @ 1:00 PM
- Primal Meetup: Dive into Primal, the slickest Nostr experience available on web, Android, and iOS. With a built-in wallet, zapping your favorite creators and friends has never been easier. The team will be on-site for hands-on demos, Q\&A, merch giveaways, and deeper discussions on building the social layer of Bitcoin.
🎙️ Nostr Talks at Bitcoin 2025
If you want to hear from the minds building decentralized social, make sure you attend these two official conference sessions:
1. FROSTR Workshop: Multisig Nostr Signing
-
🕚 Time: 11:30 AM – 12:00 PM
-
📅 Date: Wednesday, May 28
-
📍 Location: Developer Zone
-
🎤 Speaker: nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgdwaehxw309ahx7uewd3hkcqpqs9etjgzjglwlaxdhsveq0qksxyh6xpdpn8ajh69ruetrug957r3qf4ggfm (Austin Kelsay) @ Voltage\ A deep-dive into FROST-based multisig key management for Nostr. Geared toward devs and power users interested in key security.
2. Panel: Decentralizing Social Media
-
🕑 Time: 2:00 PM – 2:30 PM
-
📅 Date: Thursday, May 29
-
📍 Location: Genesis Stage
-
🎙️ Moderator: nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqy08wumn8ghj7mn0wd68yttjv4kxz7fwv3jhyettwfhhxuewd4jsqgxnqajr23msx5malhhcz8paa2t0r70gfjpyncsqx56ztyj2nyyvlq00heps - Bitcoin Strategy @ Roxom TV
-
👥 Speakers:
-
nostr:nprofile1qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcppemhxue69uhkummn9ekx7mp0qqsy2ga7trfetvd3j65m3jptqw9k39wtq2mg85xz2w542p5dhg06e5qmhlpep – Early Bitcoin dev, CEO @ Sirius Business Ltd
-
nostr:nprofile1qy2hwumn8ghj7mn0wd68ytndv9kxjm3wdahxcqg5waehxw309ahx7um5wfekzarkvyhxuet5qqsw4v882mfjhq9u63j08kzyhqzqxqc8tgf740p4nxnk9jdv02u37ncdhu7e3 – Analyst & Partner @ Ego Death Capital
Get the big-picture perspective on why decentralized social matters and how Nostr fits into the future of digital communication.
🌃 NOS VEGAS Meetup & Afterparty
Date: Wednesday, May 28\ Time: 7:00 PM – 1:00 AM\ Location: We All Scream Nightclub, 517 Fremont St., Las Vegas, NV 89101\ 🎟️ Get Tickets!
What to Expect:
-
🎶 Live Music Stage – Featuring Ainsley Costello, Sara Jade, Able James, Martin Groom, Bobby Shell, Jessie Lark, and other V4V artists
-
🪩 DJ Party Deck – With sets by nostr:nprofile1qy0hwumn8ghj7cmgdae82uewd45kketyd9kxwetj9e3k7mf6xs6rgqgcwaehxw309ahx7um5wgh85mm694ek2unk9ehhyecqyq7hpmq75krx2zsywntgtpz5yzwjyg2c7sreardcqmcp0m67xrnkwylzzk4 , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgkwaehxw309anx2etywvhxummnw3ezucnpdejqqg967faye3x6fxgnul77ej23l5aew8yj0x2e4a3tq2mkrgzrcvecfsk8xlu3 , and more DJs throwing down
-
🛰️ Live-streamed via Tunestr
-
🧠 Nostr Education – Talks by nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq37amnwvaz7tmwdaehgu3dwfjkccte9ejx2un9ddex7umn9ekk2tcqyqlhwrt96wnkf2w9edgr4cfruchvwkv26q6asdhz4qg08pm6w3djg3c8m4j , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqg7waehxw309anx2etywvhxummnw3ezucnpdejz7ur0wp6kcctjqqspywh6ulgc0w3k6mwum97m7jkvtxh0lcjr77p9jtlc7f0d27wlxpslwvhau , nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq3vamnwvaz7tmwdaehgu3wd33xgetk9en82m30qqsgqke57uygxl0m8elstq26c4mq2erz3dvdtgxwswwvhdh0xcs04sc4u9p7d , nostr:nprofile1q9z8wumn8ghj7erzx3jkvmmzw4eny6tvw368wdt8da4kxamrdvek76mrwg6rwdngw94k67t3v36k77tev3kx7vn2xa5kjem9dp4hjepwd3hkxctvqyg8wumn8ghj7mn0wd68ytnhd9hx2qpqyaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgssuy4zk , nostr:nprofile1qy28wue69uhnzvpwxqhrqt33xgmn5dfsx5cqz9thwden5te0v4jx2m3wdehhxarj9ekxzmnyqqswavgevxe9gs43vwylumr7h656mu9vxmw4j6qkafc3nefphzpph8ssvcgf8 , and more.
-
🧾 Vendors & Project Booths – Explore new tools and services
-
🔐 Onboarding Stations – Learn how to use Nostr hands-on
-
🐦 Nostrich Flocking – Meet your favorite nyms IRL
-
🍸 Three Full Bars – Two floors of socializing overlooking vibrant Fremont Street
| | | | | ----------- | -------------------- | ------------------- | | Time | Name | Topic | | 7:30-7:50 | Derek | Nostr for Beginners | | 8:00-8:20 | Mark & Paul | Primal | | 8:30-8:50 | Terry | Damus | | 9:00-9:20 | OpenMike and Ainsley | V4V | | 09:30-09:50 | The Space | Space |
This is the after-party of the year for those who love freedom technology and decentralized social community. Don’t miss it.
Final Thoughts
Whether you're there to learn, network, party, or build, Bitcoin 2025 in Las Vegas has a packed week of Nostr-friendly programming. Be sure to catch all the events, visit the Nostr Lounge, and experience the growing decentralized social revolution.
🟣 Find us. Flock with us. Purple pill someone.
-
-
 @ bf47c19e:c3d2573b
2025-05-24 16:13:51
@ bf47c19e:c3d2573b
2025-05-24 16:13:51Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Definisanje novca
- Šta je sredstvo razmene?
- Šta je obračunska jedinica?
- Šta je zaliha vrednosti?
- Zašto su važne funkcije novca?
- Novac Gubi Funkciju: Alhemičar iz Njutonije
- Eksploatacija pomoću Novca: Agri Perle
- Novac Gubi Funkciju 2. Deo: Kejnslandski Bankar
- Da li nas novac danas eksploatiše?
- Šta je novac, i zašto trebate da brinete?
- Efikasnija Ušteda Novca
- Zasluge
- Molim vas da šerujete!
Google izveštava o stalnom povećanju interesa u svetu za pitanje „Šta je novac?“ koji se postavlja iz godine u godinu, od 2004. do 2021., a sa naglim porastom nakon finansijske krize 2008. godine.
I izgleda se da niko nema dobar odgovor za to.
 Godišnji proseci mesečnih interesa za pretragu. 100 predstavlja najveći interes za pretragu tokom čitavog perioda, koji se dogodio u decembru 2019. Podaci sa Google Trends-a.
Godišnji proseci mesečnih interesa za pretragu. 100 predstavlja najveći interes za pretragu tokom čitavog perioda, koji se dogodio u decembru 2019. Podaci sa Google Trends-a.Međutim, odgovaranje na ovo naizgled jednostavno pitanje pomoći će vam da razjasnite ulogu novca u vašem životu. Jednom kada shvatite kako novac funkcioniše, tačno ćete videti i zašto svet danas ludi – i šta učiniti povodom toga. Zato hajde da se udubimo u to.
Na pitanje šta je novac, većina ljudi otvori svoje novčanike i pokaže nekoliko novčanica – “evo, ovo je novac!”
Ali po čemu se ove novčanice razlikuju od stranica vaše omiljene knjige? Pa, naravno, zavod za izradu novčanica te zemlje je odštampao te novčanice iz vašeg novčanika kako bi se oduprla falsifikovanju, i svi ih koriste da bi kupili odredjene stvari.
Međutim, Nemačka Marka imala je sva ova svojstva u prošlosti – ali preduzeća danas ne prihvataju te novčanice. Zapravo, građani Nemačke su početkom dvadesetih godina prošlog veka spaljivali papirne Marke kako bi grejali svoje domove. Marka je imala veću vrednost kao papir za potpalu nego kao novac!

1923. nemačka valuta poznata kao Marka bila je jeftinija od uglja i drveta!
Pa šta to čini novac, novcem?
Ispostavilo se da ovo nije pitanje na koje je lako dati odgovor.
Definisanje novca
Novac nije fizička stvar poput novčanice dolara. Novac je društveni sistem koji koristimo da bismo olakšali trgovinu robom i uslugama. Međutim, tokom istorije fizička monetarna dobra igrala su ključnu ulogu u društvenom sistemu novca, često kao znakovi koji predstavljaju vrednost u monetarnom sistemu. Ovaj sistem ima tri funkcije: 1) Sredstvo Razmene, 2) Obračunsku Jedinicu i 3) Zalihu Vrednosti.
Odakle dolaze ove funkcije, i zašto su one vredne?
Šta je sredstvo razmene?
Sredstvo razmene je neko dobro koje se obično razmenjuje za drugo dobro. Najčešće objašnjenje za to kako su se pojavila sredstva razmene glasi otprilike ovako: Boris ima ječam i želeo bi da kupi ovcu od Marka. Marko ima ovce, ali želi samo piliće. Ana ima piliće, ali ona ne želi ječam ili ovce.
To se naziva problem sticaja potreba: dve strane moraju da žele ono što druga ima da bi mogle da trguju. Ako se želje dve osobe ne podudaraju, oni moraju da pronađu druge ljude sa kojima će trgovati dok svi ne pronađu dobro koje žele.
 Ljudi koji trguju robom i uslugama moraju da imaju potrebe koje se podudaraju.
Ljudi koji trguju robom i uslugama moraju da imaju potrebe koje se podudaraju.Vremenom, veoma je verovatno da će se određena vrsta robe, poput pšenice, pojaviti kao sredstvo razmene jer su je mnogi ljudi želeli. Uzimajući pšenicu kao primer: pšenica je rešila “sticaje potreba” u mnogim zanatima, jer čak i ako onaj koji prima pšenicu a nije želeo da je koristi za sebe, znao je da će je neko drugi želeti.
Ovo nazivamo prodajnost imovine.
Pšenica je dobar primer dobra za prodaju jer svi moraju da jedu, a od pšenice se pravi hleb. Pšenica ima vrednost kao sastojak hleba i kao dobro koje olakšava trgovinu rešavanjem problema „sticaja potreba“.
Razmislite o svojoj želji da dobijete više novčanica u eurima ili drugoj valuti. Ne možete da jedete novčanice da biste preživeli, a i ne bi vam bile od velike koristi ako poželite da ih koristite kao građevinski materijal za vašu kuću. Međutim, znate da sa tim novčanicama možete da kupite hranu i kuću.
Stvarne fizičke novčanice su beskorisne za vas. Novčanice su vam dragocene samo zato što će ih drugi prihvatiti za stvari koje su vama korisne.
Tokom dugog perioda istorije, novac je evoluirao do te mere da monetarno dobro može imati vrednost, a da to dobro ne služi za bilo koju drugu ‘suštinsku’ upotrebu, poput hrane ili energije. Umesto toga, njegova upotreba je zaliha vrednosti i jednostavna zamena za drugu robu u bilo kom trenutku koji poželite.
Šta jedno dobro čini poželjnijim i prodajnijim od drugog dobra?
Deljivost
Definicija: Sposobnost podele dobra na manje količine.
Loš Primer: Dijamante je teško podeliti na manje komade. Za zajednicu od hiljada ljudi koji dnevno izvrše milione transakcija, dijamanti čine loše sredstvo razmene. Previše su retki i nedeljivi da bi se koristili za mnoge transakcije.
Ujednačenost
Definicija: Sličnost pojedinačnih jedinica odredjenog dobra.
Loš Primer: Krave nisu ujednačene – neke su veće, neke manje, neke bolesne, neke zdrave. Sa druge strane, unca čistog zlata je jednolična – jedna unca je potpuno ista kao sledeća. Ovo svojstvo se takođe često naziva zamenljivost.
Prenosivost
Definicija: Lakoća transporta dobra.
Loš Primer: Krava nije baš prenosiva. Zlatnici su prilično prenosivi. Papirne novčanice su još prenošljivije. Knjiga u kojoj se jednostavno beleži vlasništvo nad tim vrednostima (poput Rai kamenog sistema ili digitalnog bankovnog računa) je neverovatno prenosiva, jer nema fizičkog dobra koje treba nositi sa sobom za kupovinu. Postoji samo sistem za evidentiranje vlasništva nad tim vrednostima u nematerijalnom obliku.
Kako dobro postaje sredstvo razmene?
Dobra postaju, i ostaju sredstva razmene zbog svoje univerzalne potražnje, takođe poznate kao njihova prodajnost, čemu pomažu svojstva koja su gore nabrojana.
Mnogo različitih dobara mogu u različitoj meri delovati kao sredstva razmene u ekonomiji. Danas, naša globalna ekonomija koristi valute koje izdaju države, zlato, pa čak i robu poput nafte kao sredstvo razmene.
Šta je obračunska jedinica?
Stvari se komplikuju kada u ekonomiji postoji mnogo robe koja se prodaje. Čak i sa samo 5 dobara, postoji 10 “kurseva razmene” između svake robe kojih svi u ekonomiji moraju da se sete: 1 svinja se menja za 15 pilića, 1 pile se menja za 15 litara mleka, desetak jaja se menja za 15 litara mleka, i tako dalje. Ako ekonomija ima 50 dobara, među njima postoji 1.225 “kurseva razmene”!
Sredstvo za merenje vrednosti
Zamislite obračunsku jedinicu kao sredstvo za merenje vrednosti. Umesto da se sećamo vrednosti svakog dobra u poredjenju sa drugim dobrima, mi samo treba da se setimo vrednosti svakog dobra u poredjenju sa jednim dobrom – obračunskom jedinicom.
Umesto da se setimo 1.225 kurseva razmene kada imamo 50 proizvoda na tržištu, mi treba da zapamtimo samo 50 cena.
Na primer, ne treba da se sećamo da litar mleka vredi 1/15 piletine ili desetak jaja, možemo da se samo setimo da litar mleka košta 1USD.
Poređenje dobara je lakše sa obračunskom jedinicom
Obračunska jedinica takođe olakšava upoređivanje vrednosti i donošenje odluka. Zamislite da pokušavate da kupite par Nike Air Jordan patika kada ih jedan prodavac prodaje za jedno pile, a drugi za 50 klipova kukuruza.
Šta je zaliha vrednosti?
Do sada smo gledali samo primere transakcija koje se odvijaju u određenom trenutku u vremenu.
Međutim, ljudi vrše transakcije tokom vremena – oni štede novac i troše ga kasnije. Da bi odredjeno dobro moglo da funkcioniše pravilno kao monetarno dobro, ono treba da održi vrednost tokom vremena.
Novac koji vremenom dobro drži vrednost daje njegovom imaocu više izbora kada će taj novac da potroši.
To znači da prodajnost dobra uključuje njegovu sposobnost da održi vrednost tokom vremena.
Šta jedno dobro čini boljom zalihom vrednosti od drugog dobra?
Trajnost
Definicija: Sposobnost dobra da vremenom zadrži svoj oblik.
Loš Primer: Jagode čine lošu zalihu vrednosti jer se lako oštete i brzo trunu.
Odluka je daleko lakša ako jedan prodavac naplaćuje 150 USD, a drugi 200 USD – odmah je očigledno koja je bolja ponuda jer su vrednosti izražene u istoj jedinici.
Teške za Proizvodnju
Definicija: Teškoće koje ljudi imaju u proizvodnji veće količine dobra.
Loš Primer: Papirne novčanice predstavljaju lošu zalihu vrednosti jer banke i vlade mogu jeftino da ih naprave.
Sa zlatom je suprotno – u ponudi se nalazi ograničena količina uprkos velikoj potražnji za njim, jednostavno zato što ga je vrlo teško iskopati iz zemlje. Ova ograničena ponuda osigurava da svaka jedinica zlata održi vrednost tokom vremena.
Kako dobra postaju zalihe vrednosti?
Dobro postaje zaliha vrednosti ako se vremenom pokaže trajnim i teškim za proizvodnju.
Samo će vreme pokazati da li je neko dobro zaista trajno i da li ga je teško proizvesti. Zbog toga neki oblici novca su postojali vekovima pre nego što je neko otkrio način da ih proizvede više, i na kraju se to dobro više nije koristilo kao novac.
Ovo je priča o školjkama, Rai kamenju i mnogim drugim oblicima novca tokom istorije.
Zlato je primer dobra koje je hiljadama godina služilo kao dobra zaliha vrednosti. Zlato se ne razgrađuje tokom vremena i još uvek ga je teško proizvesti. Hiljadama godina alhemičari su bezuspešno pokušavali da sintetišu zlato iz jeftinih materijala.
Čak i sa današnjim naprednim rudarskim tehnikama, svake godine svi svetski rudnici zlata zajedno mogu da proizvedu samo 2% od ukupne ponude zlata u prometu.
Teškoće u proizvodnji zlata daju izuzetno visok odnos “zaliha i protoka”: zaliha je broj postojećih jedinica, a protok su nove jedinice stvorene tokom određenog vremenskog perioda. Svake godine se stvori vrlo malo novih jedinica zlata, iako je potražnja za zlatom obično vrlo velika.
Kombinujući ovo sa deljivošću, ujednačenošću i prenosivošću zlata, nije ni čudo što je zlato čovečanstvu služilo kao monetarno dobro tokom poslednjih 5.000 godina. Pošto je zlato teško proizvesti, možemo ga nazvati teškim novcem (hard money).
Kao rezultat toga, svoju vrednost je u velikoj meri zadržao kroz milenijume. Cena većine dobara i usluga u pogledu zlata zapravo se vremenom smanjivala kao rezultat tehnoloških inovacija, koje sve proizvode čine jeftinijim.
Uzmimo na primer cene hrane prema praćenju Kancelarije za hranu i poljoprivredu UN-a: sa obzirom na skokove u poljoprivrednoj tehnologiji tokom poslednjih 60 godina, cene hrane drastično su pale kada se procenjuju u zlatu. To čak i važi uprkos činjenici da obični ljudi retko koriste zlato za kupovinu stvari.
 Cene hrane su padale u pogledu zlata tokom proteklih 60 godina, i mnogo pre toga (FAO Indeks Cena Hrane u Zlatu)
Cene hrane su padale u pogledu zlata tokom proteklih 60 godina, i mnogo pre toga (FAO Indeks Cena Hrane u Zlatu)Zaliha vrednosti omogućava ljudima da uštede novac kako bi mogli da ga ulažu u pokretanje preduzeća i obrazovanje, povećavajući produktivnost društva.
Monetarna dobra koja dobro čuvaju vrednost takođe podstiču dugoročniji pogled na život, ili kratke vremenske preference. Pojedinac može da radi 10 godina, uštedi odredjeno monetarno dobro koje je dobra zaliha vrednosti, i nema potrebe da se plaši da će njegova ušteđevina biti izbrisana krahom tržišta ili povećanjem ponude tog dobra.
Zašto su važne funkcije novca?
Kada neki oblik novca izgubi bilo koju od svojih važnih funkcija kao što su sredstvo razmene, obračunska jedinica i zaliha vrednosti, celokupna ekonomija i društvo mogu da se rastrgnu.
Tokom istorije često vidimo grupe ljudi koje eksploatišu druge iskorišćavajući nesporazume o novcu i važnosti njegovih funkcija.
Sledeće, proći ću kroz istoriju novca, prvo hipotetički da bih ilustrovao poentu, a zatim ću preći na stvarne istorijske primere. Kroz ove primere videćemo štetne efekte na društva u slučajevima kada se izgubi samo jedna od tih ključnih funkcija novca.
Novac Gubi Funkciju: Alhemičar iz Njutonije
Kroz istoriju, mnoga dobra su dolazila i odlazila kao oblici novca. Na žalost, kada se neki oblik novca ukine, ponekad postoji grupa ljudi koja eksploatiše drugi oblik manipulišući tim novcem.
Hajde da pogledamo hipotetičko selo zvano Njutonija da bismo razumeli kako dolazi do ove eksploatacije.
Zelene perle postaju Novac
Tokom stotina godina ribolova u obližnjoj reci, stanovnici Njutonije sakupljali su zelene perle iz vode. Zrnca su mala, lagana, izdržljiva, jednolična i retko se pojavljuju u reci. Ljudi prvo priželjkuju perle zbog svoje lepote. Na kraju, seljani shvataju da svi drugi žele perle – one se vrlo lako mogu prodati. Zrnca uskoro postaju sredstvo razmene i obračunska jedinica u selu: pile je 5 zrna, vreća jabuka 2 zrna, krava 80 zrna.
Ukupna ponuda perli je prilično konstantna i cene se vremenom ne menjaju mnogo. Seoski starešina je uveren da može da se opustiti u poslednjim danima živeći od svoje velike zalihe perli.
Alhemičar stvara više perli
Seoski alhemičar je poželeo da bude bogat čovek, ali nije voleo da vredno radi na tome. Umesto da traži perle u reci ili da prodaje vrednu robu drugim seljanima, on sedeo je u svojoj laboratoriji. Na kraju je otkrio kako da lako stvori stotine perli sa malo peska i vatre.
Seljani koji su tragali za perlama u reci bili su srećni ako bi svaki dan pronašli po 1 zrno. Alhemičar je mogao da proizvede stotine uz malo napora.
Alhemičar troši svoje perle
Budući da je bio prilično zao, alhemičar nije svoj metod pravljenja zrna delio ni sa kim drugim. Stvorio je sebi još više perli i počeo da ih troši za dobra na tržištu u Njutoniji. Tokom sledećih meseci, alhemičar je kupio farmu pilića, nekoliko krava, finu svilu, posteljine i ogromno imanje. On je imao priliku da kupi ova dobra po normalnim cenama na tržištu.
Alhemičarevo trošenje ostavljalo je seljanima mnogo perli, ali malo njihove vredne robe.
Svi seljani su se osećali bogatima – imali su tone perli! Međutim, polako su primetili da i svi ostali takodje imaju tone.
Cene počinju da rastu
Uzgajivač pilića primetio je da sva roba koju je trebalo da kupi na pijaci poskupela. Džak jabuka sada se prodaje za 100 perli – 50 puta više od njihove cene pre nekoliko meseci!
Iako je sada imao hiljade perli, uskoro bi mogao da ostane bez njih zbog ovih cena. Pitao se – da li zaista može sebi da priušti da prodaje svoje piliće za samo 5 perli po komadu? Morao je i on da podigne svoje cene.
Jednostavno rečeno, kao rezultat alhemičarevog trošenja njegovih novostvorenih perli, bilo je previše perli koje su jurile premalo dobara – pa su cene porasle.
Kupci robe bili su spremni da potroše više perli da bi kupili potrebna dobra. Prodavci robe su trebali da naplate više da bi bili sigurni da su zaradili dovoljno da kupe potrebna dobra za sebe.
Budući da su cene svih dobara porasle, možemo reći da se vrednost svake perle smanjila.
Nejednakost bogatstva raste
Seoski starešina, koji je vredno radio da sačuva hiljade perli, sada se našao osiromašenim i gladnim. U međuvremenu, alhemičar je udobno sedeo na svom velikom imanju sa kravama, pilićima i slugama koji su se brinuli za svaki njegov hir.
Alhemičar je efikasno ukrao bogatstvo celog sela, tako što je jeftino proizvodio perle i koristio ih za kupovinu vredne robe.
Ono što je najvažnije, kupio je robu pre nego što je tržište shvatilo da je više perli u opticaju i da ima manje robe, što je dovelo do rasta cena. Ova dodatna proizvodnja perli nije dodala korisnu robu ili usluge selu.
Eksploatacija pomoću Novca: Agri Perle
Nažalost, priča o alhemičaru iz Njutonije nije u potpunosti hipotetička. Ovaj prenos bogatstva kroz stvaranje novca ima istorijske i moderne presedane.
Na primer, afrička plemena su nekada koristila staklene perle, poznate kao “agri perle”, kao sredstvo razmene. U to vreme plemenskim ljudima je bilo veoma teško da prave staklene perle, i one su predstavljale težak novac unutar njihovog plemenskog društva.
Niko nije mogao jeftino da proizvede perle i koristiti ih za kupovinu skupe, vredne robe poput kuća, hrane i odeće.
Sve se promenilo kada su stigli Evropljani, i primetili upotrebu staklenih perli kao novca.
U to vreme, Evropljani su mogli jeftino da stvaraju staklo u velikim količinama. Kao rezultat toga, Evropljani su počeli tajno da uvoze perle i koriste ih za kupovinu dobara, usluga i robova od Afrikanaca.
Vremenom se iz Afrike izvlačila vredna roba i ljudi, dok je plemenima ostajalo mnogo perli i malo robe.
Perle su izgubile veći deo vrednosti zbog inflacije uzrokovane snabdevanjem od strane Evropljana.
Rezultat je bio osiromašenje afričkih plemena i bogaćenje Evropljana, kako to ovde objašnjava monetarni istoričar Bezant Denier.
Dragocena roba je kupljena jeftino proizvedenim monetarnim dobrom.
Profitiranje na proizvodnji novca: Emisiona dobit
Ova priča ilustruje kako se bogatstvo prenosi kada jedna grupa može jeftino da proizvodi monetarno dobro.
Razlika između troškova proizvodnje monetarnog dobra i vrednosti tog monetarnog dobra poznata je kao emisiona dobit, eng. seignorage.
Kada je monetarno dobro mnogo vrednije od troškova proizvodnje, ljudi će proizvesti više od monetarnog dobra da bi uhvatili profit od emisione dobiti.
Na kraju će ova povećana ponuda dovesti do pada vrednosti monetarnog dobra. To je zbog zakona ponude i potražnje: kada se ponuda povećava, cena (poznata i kao vrednost) dobra opada.
Novac Gubi Funkciju 2. Deo: Kejnslandski Bankar
U priči o Njutoniji, alhemičar je otkrio način da se od malo peska jeftino stvori više zelenih perli. To se u stvarnosti odigralo kroz trgovinu između Evropljana i Afrikanaca, pričom o agri perlama. Međutim, ove priče su pomalo zastarele – mi više ne trgujemo robom za perle.
Da bismo nas doveli do modernog doba, hajde da promenimo neka imena u našoj priči:
- Selo Njutonija postaje država koja se zove Kejnsland
- Alhemičar postaje bankar
- Seoski starešina postaje penzioner
- Zelene perle postaju zlato, koje niko ne može jeftinije da stvori – čak ni bankar.
Bankar Menja Papirne Novčanice za Zlato
Kao i u stvarnosti, bankar u ovoj priči nema formulu ili trik da stvori više zlata. Međutim, bankar bezbedno čuva zlato u vlasništvu svakog građanina Kejnslanda. Bankar daje svakom građaninu po jednu potvrdu za svaku uncu zlata koje ima u svom trezoru.
Te potvrde se mogu iskoristiti u bilo koje vreme za stvarno zlato. Papirne potvrde ili novčanice su mnogo pogodnije za plaćanje nego nošenje zlata kroz supermarket.
Građani su srećni – oni imaju prikladno sredstvo plaćanja u vidu bankarevih novčanica, i znaju da niko ne može da ukrade njihovo bogatstvo falsifikujući više zlata.
Građani na kraju počinju da plaćaju u potpunosti papirnim novčanicama, ne trudeći se nikad da zamene svoje novčanice za zlato. Na kraju, novčanice postaju “dobre kao i zlato” – svaka predstavlja fiksnu količinu zlata u bankarevom trezoru.
Ukupno kruži 1.000.000 novčanica, od kojih je svaka otkupljiva za jednu uncu zlata. 1.000.000 unci zlata sedi u bankarevom trezoru. Svaka novčanica je u potpunosti podržana u zlatu.
Starešina koji je sačuvao sve svoje perle u priči o Njutoniji sada je penzioner u Kejnslandu, koji svoje zlato drži u banci i planira da ugodno živi od novčanica koje je dobio zauzvrat.
Hajde da u ovu priču dodamo i novi lik: premijera Kejnslanda. Premijer naplaćuje porez od građana i koristi ga za plaćanje javnih usluga poput policije i vojske. Premijer takođe drži vladino zlato kod bankara.
Bankar Menja Papirne Novčanice za Dug
Premijer želi da osigura da nacionalno zlato ostane na sigurnom, pa banku štiti policijom. Bankar i premijer se zbog toga zbližavaju, pa premijer traži uslugu. Traži od bankara da kreira 200.000 novčanica za premijera, uz obećanje da će mu premijer vratiti za pet godina. Premijeru su novčanice potrebne za finansiranje rata. Građani Kejnslanda borili su se protiv većih poreza zbog finansiranja rata, pa je morao da se obrati bankaru.
Bankar se slaže da izradi novčanice, ali pod jednim uslovom: bankar uzima deo od 10.000 novčanica za sebe. Premijer prihvata posao kojim bankar ’kupuje državni dug’. Sada je u opticaju 1.200.000 novčanica, potpomognutih kombinacijom 1.000.000 unci zlata i ugovorom o dugu sa vladom za 200.000 novčanica.
Premijer troši svoje nove novčanice na bombe kupujući ih od dobavljača iz domaće vojne industrije, a bankar sebi kupuje veliki luksuzni stan.
Dobavljač iz vojne industrije koristi sve nove novčanice koje je dobio od premijera da kupi amonijum nitrat (đubrivo koje se koristi u bombama) za proizvodnju bombi. Sve njegove kupovine povećavaju cenu đubriva za uzgajivače pšenice u Kejnslandu, pa oni podižu cenu pšenice.
Kao uzrok toga, pekar koji kupuje pšenicu treba da podigne cenu svog hleba da bi ostao u poslu. Na taj način cene u Kejnslandu počinju da rastu, baš kao što su to činile u Njutoniji kada su nove perle ušle u opticaj.
Papirne Novčanice Više Ne Predstavljaju Zlato
Penzioner nailazi na finansijski časopis u kojem se pominje premijerov dogovor da se zaduži za finansiranje rata. Obzirom da je mudar, on zna da bombe loše vraćaju ulaganje i sumnja da će premijer ikada da vrati svoj dug.
Ako on ‘podmiri’ svoj dug, to bi ostavilo 1.200.000 novčanica u opticaju sa samo 1.000.000 unci zlata da bi ih podržalo, obezvređujući njegovu ušteđevinu. Već oseća stisak u džepu zbog porasta cena, i on odlučuje da se uputi u lokalnu banku i preda svoje novčanice i zameni ih za zlato, koje niko ne može da napravi u većoj količini.
Kada penzioner stigne u banku, on zatiče i mnoge druge okupljene oko banke. Svi oni se nadaju da će uzeti zlato koje predstavljaju njihove novčanice. Građani Kejnslanda sa pravom se plaše da njihove novčanice gube na vrednosti – oni to već osećaju zbog porasta cena.
Vrata su zaključana, sa obaveštenjem bankara na njima:
Po nalogu premijera, onom koji se plaši za stabilnost ove bankarske institucije, ova banka više neće podržavati konvertibilnost papirnih novčanica u zlato. Hvala vam!
Gomila se razilazi, ostavljena sa jednim izborom: da zadrže svoje novčanice, koje sada vrede manje od 1 unce zlata. Građani sa dovoljno finansijske stabilnosti odlučuju da ulože svoje novčanice u kupovinu akcija banke i kompanija vojne industrije, koje dobro posluju jer mogu da kupuju stvari pre nego što se povećaju tržišne cene.
Mnogi ljudi nisu u mogućnosti da investiraju – oni moraju da gledaju kako njihove zarade stagniraju i kako njihova ušteđevina polako ali sigurno gubi vrednost.
Penzioner, koji se nadao da će živeti od novčanica koje je zaradio tokom svojih 40 radnih godina, sada 40 sati nedeljno provodi iza kase u lokalnoj prodavnici, pitajući se gde je sve pošlo po zlu.
Dug Nikada Nije Otplaćen
Prošlo je nekoliko godina, a premijerov dug prema banci dolazi na naplatu. Budući da je potrošio svih 200.000 novčanica na bombe, koje nemaju baš dobar povraćaj ulaganja, on nema novčanice koje može da vrati banci. Plus, premijer želi da kupi još bombi za svoj rat.
Bankar uverava premijera da je sve u redu. Bankar će napraviti novi ugovor o dugu za 600.000 novčanica, koji bi trebao da stigne na naplatu u narednih 5 godina. Premijer može da iskoristi 200.000 od tih novih 600.000 novčanica da vrati svoj prvobitni dug prema banci, zadrži još 300.000 da kupi još bombi i da 100.000 bankaru da bi mu platio njegove usluge.
To nastavlja da se dešava – svaki put kada dug dospeva na naplatu, bankar stvara više novčanica za vraćanje starijih dugova i daje premijeru još više novca za trošenje. Ovaj ciklus se nastavlja.
Šta se dešava u Kejnslandu?
- Oni koji prvi dobiju nove novčanice, gledaju kako se njihovo bogatstvo povećava
- To uključuje bankara, premijera, vladu i sve one koji mogu da pristupe mogućnostima za investiranje u preduzeća koja prva dobiju nove novčanice (finansijske, vojne itd.).
- Cene roba rastu
- Cene se ne povećavaju ravnomerno – one se povećavaju gde god nove novčanice prvo uđu u ekonomiju i od tog trenutka imaju efekat talasa na tržišta. U našem primeru prvo raste cena amonijum nitrata, zatim cena pšenice, pa cena hleba. A tek na kraju zarade običnih ljudi.
- Štednja i životni standard opšte populacije se smanjuju
- Najviše pate oni koji žive od plate do plate i ne mogu da ulažu. Čak i oni koji su u mogućnosti da investiraju podložni su hirovima tržišta. Mnogi su prisiljeni da prodaju svoje investicije po niskim cenama tokom pada tržišta samo da bi platili svoje dnevne potrebe.
- Razlika u prihodima i bogatstvu između bogatih i siromašnih se povećava
- Bogatstvo opšte populacije se smanjuje, dok se bogatstvo onih koji su blizu mesta gde se troše nove novčanice povećava. Rezultat je disparitet koji se vremenom samo proširuje.
Da li nas novac danas eksploatiše?
Priča o Njutoniji i stvarna priča o agri perlama u Africi deluju pomalo zastarelo. Priča o Kejnslandu, međutim, deluje neobično poznato. U našem svetu cene robe uvek rastu, i vidimo rekordne nivoe nejednakosti u bogatstvu.
U poslednjem odeljku ovog našeg članka Šta je novac, proći ću kroz nastanak bankarstva i korake koji su bili potrebni da se dođe do današnjeg sistema, gde banke i vlade sarađuju u kontroli ekonomije i samog novca.
Šta su banke, i odakle su one došle?
Pojava bankarstva verovatno se dogodila da bi olakšala poljoprivrednu trgovinu i da bi povećala pogodnosti. Iako su se mnoga društva na kraju konvergirala ka upotrebi zlata i srebra kao novca, ovi metali su bili teški i opasni za nošenje kao tovar. Međutim, u mnogim slučajevima ih nije ni trebalo prevoziti. Uzmite ovaj primer:
Grad treba da plati poljoprivrednicima na selu za žito, a poljoprivrednici gradskoj vojsci za zaštitu od varvara. U ovom dogovoru zlato se kreće u oba smera: prema poljoprivrednicima u selu kako bi im se platilo žito, i nazad u grad da bi se platila vojska. Da bi olakšali ove transakcije, preduzetnici su stvorili koncept banke. Banka je zlato čuvala u sigurnom trezoru i izdavala novčanice od papira. Svaka priznanica je predstavljala potvrdu da njen imaoc poseduje određenu količinu zlata u banci. Imaoc novčanice je u svako doba mogao da uzme svoje zlato nazad vraćanjem te novčanice banci.
Korisnici banke mogli su lakše da trguju sa novčanicama od papira, i onaj koji poseduje novčanice mogao je da preuzme njihovo fizičko zlato u bilo kom trenutku. To je te novčanice učinilo “dobrim kao i zlato”.
Banke su izdržavale svoje poslovanje naplaćujući od kupaca naknadu za skladištenje zlata ili pozajmljivanjem dela zlata i zaračunavanjem kamata na njega. Trgovina na ovaj način je mogla da se odvija sa laganim novčanicama od papira umesto sa teškim vrećama zlatnika.
Ovakva praksa sa transakcijama, korišćenjem papirne valute potpomognute monetarnim dobrima, verovatno je započela u Kini u 7. veku.
Na kraju se proširila Evropom 1600-ih, a svoj zalet dobila je u Holandiji sa bankama poput Amsterdamske Wisselbanke. Novčanice Wisselbank-e često su vredele više od zlata koje ih je podržavalo, zbog dodane vrednosti njihovih pogodnosti.
Uspon nacionalnih ‘centralnih banaka’
Tokom vekova, zlato je počelo da se sakuplja u trezorima banaka, jer su ljudi više voleli pogodnosti transakcija sa novčanicama.
Na kraju, nacionalne banke u vlasništvu vlada preuzele su ulogu čuvanja zlata od privatnih banaka koje su započeli preduzetnici.
Nacionalne papirne valute potpomognute zlatnim rezervama u nacionalnim bankama zamenile su novčanice iz privatnih banaka. Sve nacionalne valute bile su jednostavno potvrde za zlato koje se nalazilo u trezoru nacionalne banke.
Ovaj sistem je poznat kao zlatni standard – sve valute su jednostavno predstavljale različite težine zlata.
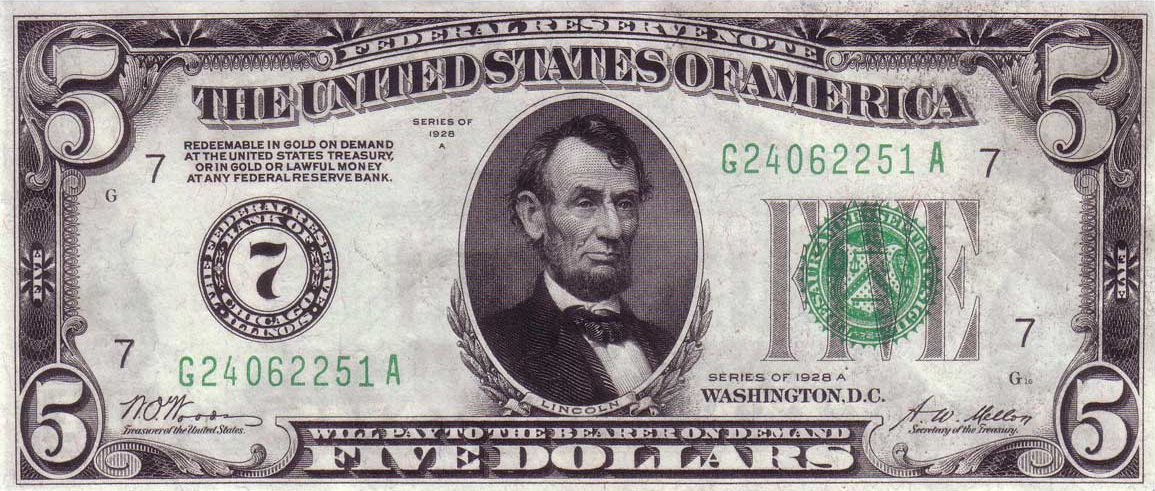 U gornjem levom uglu novčanice možete videti da piše da je novčanica “zamenljiva za zlato”. Savremeni dolari nemaju ovaj natpis, ali inače izgledaju vrlo slično. Izvor
U gornjem levom uglu novčanice možete videti da piše da je novčanica “zamenljiva za zlato”. Savremeni dolari nemaju ovaj natpis, ali inače izgledaju vrlo slično. IzvorZlatni sistem je postojao veći deo vremena, sve do Prvog svetskog rata. Vladama je bilo teško da prikupe novac za ovaj rat putem poreza, pa su morale da budu kreativne.
Kada vlade troše više nego što zarađuju na porezima, to se naziva deficitna potrošnja.
Kako vlade mogu ovo da urade? Vlade to rade tako što pozajmljuju novac prodavajući svoj dug.
Tokom Prvog svetskog rata, vlade su građanima i preduzećima prodavale vrstu duga koja se naziva ratna obveznica. Kada građanin kupi ratnu obveznicu, on preda svoj novac vladi i dobije papir u kojem je stajalo vladino obećanje da će vlasniku obveznice vratiti novac, plus kamate, za nekoliko godina.
Plakat koji obaveštava građane, tražeći od njih da kupe ratne obveznice – što predstavlja zajam vladi. Izvor
Centralne banke ‘monetizuju’ državni dug
Međutim, građani i preduzeća nisu bili voljni da kupe dovoljno ratnih obveznica za finansiranje Prvog svetskog rata.
Vlade se nisu predale – pa su zatražile od svojih nacionalnih ‘centralnih banaka’ da one kupe ove obveznice. Centralne banke su otkupile obveznice, ali ih nisu platile valutom potpomognutom postojećim zlatnim rezervama, kao što su to činili građani i banke prilikom kupovine obveznica.
Centralne banke su umesto toga davale vladi novu, sveže štampanu papirnu valutu potpomognutu samo obveznicom. Ovu valutu podržalo je samo obećanje da će im vlada vratiti dugove. Ovo je poznato kao monetizacija duga.
Budući da su ratne obveznice i valuta samo komadi papira, one su lake i jeftine za proizvodnju i mogu se napraviti u ogromnim količinama. Ono što ograničava proizvodnju i jednog i drugog je poverenje.
Ima smisla da se neko rastane od svog teško stečenog novca da kupi državnu obveznicu, samo ako veruje da će vlada da vrati svoj dug, plus kamate. Centralna banka je “krajnji kupac”, što znači da će ona da kupi državne obveznice kada to niko drugi neće da uradi.
Zapamtite, centralnu banku gotovo da ništa ne košta da kupi državne obveznice, jer oni sami štampaju valutu da bi ih kupili.
Zamislite da pridjete najskupljem automobilu u autosalonu – koji košta 100.000 USD. Mislite da je automobil lep, ali taj novac biste radije potrošili na lepši stan – tako da ste spremni da platite samo 40.000 USD za taj auto.
Sada, hajde da zamislimo da imate štampač za novac i da vas košta samo 50 USD za mastilo i papir da bi ištampali 1.000.000 USD. Vi biste odmah kupili auto, čak i ako biste morali da se cenkate sa drugim čovekom, i da ga na kraju platite 150.000 USD!
Ista stvar se dešava kada centralna banka kupuje obveznice (dugove) od vlade. Centralna banka može da stvori valutu toliko jeftino, da su spremni da plate i više nego što bi drugi platili ove obveznice i nastaviće da ih kupuju čak i kada niko drugi ne bude želeo.
Monetizacija duga uzrokuje inflaciju
Kada centralne banke monetizuju državni dug, funkcija novca kao zalihe vrednosti počinje da se nagriza. Vlada troši novi novac koji je dobila od svoje centralne banke na ratnu robu, obroke i još mnogo toga.
Cene roba rastu od ove novoštampane valute koja kruži kroz ekonomiju. Kada se cene povećavaju, to znači da se vrednost svake jedinice valute smanjuje. Svi koji drže valutu sada imaju manje vrednosti. Danas to nazivamo sporim gubitkom funkcije zalihe vrednosti u novčanoj inflaciji.
Za Nemačku nakon Prvog svetskog rata monetizacija duga izazvala je totalni slom Nemačke ekonomije i stvorila uslove za rast fašizma.
Kao deo sporazuma o prekidu vatre koji je okončao Prvi svetski rat, Nemačka je pobednicima morala da plati ogroman novac. Nemačkoj vladi je bio preko potreban novac, pa su prodale obveznice (dug) Rajhsbanci, nemačkoj centralnoj banci.
Ovaj postupak doveo je do toga da je vlada štampala toliko maraka (tadašnja nemačka valuta) da je tempo inflacije u Nemačkoj ubrzan u hiperinflaciju početkom 1920-ih. Cena vekne hleba za samo 4 godine popela se sa 1,2 marke na 428 biliona maraka.
Tokom i posle Prvog svetskog rata, SAD, Britanija, Francuska i mnoge druge vlade pratile su Nemačku u štampanju valute potpomognute državnim dugom.
To je dovelo do toga da su građani želeli da svoju papirnu valutu zamene za zlato, baš kao i penzioner iz priče o Kejnslandu.
Međutim, mnoge vlade su suspendovale konvertibilnost svojih valuta u zlato. Ovim potezom vlade su primorale svoje građane da drže nacionalnu papirnu valutu i gledaju kako se njihova ušteda smanjuje u vrednosti.
Da bi mogle da nastave da štampaju novac i da bi ga trošile na nepopularne programe za koje nisu mogle da skupljaju poreze za finansiranje – poput ratova.
Bretton Woods: Novi monetarni sistem
Nakon razaranja koja su donela dva svetska rata, vlade su uspostavile novi globalni monetarni sistem prema Bretton Woods-ovom sporazumu iz 1944. godine.
Prema ovom sporazumu, valuta svake države konvertovala se po fiksnom kursu sa američkim dolarom. Američki dolar je zauzvrat predstavljao zlato po stopi od 35 USD za jednu trojsku uncu zlata*.
Sve globalne valute su stoga još uvek bile jednostavna reprezentacija zlata, putem američkih dolara kao posrednika. Redovni građani više nisu mogli da otkupljuju svoje valute za zlato iz Sjedinjenih Država. Međutim, strane centralne banke mogle bi da dođu u Sjedinjene Države da bi zamenile dolare za zlato po stopi od 35 USD za jednu uncu zlata.
Međutim, vlada Sjedinjenih Država nije uvek držala dovoljno zlata da podrži sve dolare u opticaju. Američka vlada nastavila je da finansira proširene socijalne i vojne programe prodajom državnog duga svojoj centralnoj banci, Federalnim rezervama, koja je povećala ponudu dolara bez povećanja ponude zlata koja podupire te dolare.
*Trojna unca je standardna mera čistog zlata i ima malo veću težinu od normalne unce.
Propast Bretton Woods-a
Tokom 1970-ih, sve veći troškovi rata u Vijetnamu i stranih vlada koje su otkupljivale svoje dolare za zlato, stvorili su pritisak na Trezor Sjedinjenih Država.
Ponuda dolara je porasla, dok je zlato u posedu Sjedinjenih Država opalo. Od 1950. pa do početka 1970-ih, rezerve zlata koje je držala vlada Sjedinjenih Država smanjile su se za više od 50%, sa 20 metričkih tona na samo 8 metričkih tona.
Godine 1970. država je imala zlata u vrednosti od samo 12 biliona dolara po zvaničnom kursu od 35 dolara za trojsku uncu zlata. Tokom ovog istog vremenskog perioda, ukupna ponuda američkih dolara otišla je sa oko 32 biliona USD na skoro 70 biliona USD.

Zvanične rezerve zlata u SAD-u su naglo padale od 1950. do 1970. godine, dok su se dolari u opticaju povećavali. Izvor: Wikipedia, DollarDaze.org
Američka vlada nije bila u stanju da potkrepi dolare zlatom od 35 dolara po trojnoj unci, što dovelo do rizika za čitav globalni monetarni sistem.
Početkom sedamdesetih godina, trojna unca zlata trebala je da vredi 200 USD da bi u potpunosti podržala sve američke dolare u opticaju. Rečeno na drugi način, Sjedinjene Države su pokušavale da kažu svetu da jedan dolar vredi 1/35 trojne unce zlata, ali u stvarnosti dolar je vredeo samo 1/200 trojne unce.
Kad su strane vlade trebale da pribave dolare za međunarodnu trgovinu i rezerve, bile su opelješene. Francuska vlada je to shvatila šezdesetih godina prošlog veka i počela je da prodaje svoje američke dolare za zlato po zvaničnom kursu od 35 dolara za trojsku uncu zlata.
Zemlje su počinjale da se bude iz šeme američke vlade. SAD su krale bogatstvo putem emisione dobiti, prodajući dolare za 1/35 trojne unce zlata, kada su vredeli samo 1/200 trojske unce.
Nixonov Šok ulazi u ’tradicionalni’ novac
Da bi kuća od karata mogla da ostane na mestu, predsednik Nixon je 1971. najavio da će američka vlada privremeno da obustavi konvertibilnost dolara u zlato.
Strane vlade više nisu mogle da polažu pravo na zlato svojim papirnim dolarima, a dolar više nije bio “poduprt” zlatom. Nixon je tvrdio da će ovo stabilizovati dolar.
50 godina kasnije, kristalno je jasno da je ovo samo pomoglo dolaru da izgubi vrednost i da ovaj “privremeni” program još uvek traje.
Pre 1971. godine, sve globalne valute bile su vezane za američki dolar putem Bretton Woods-ovog sporazuma. Kada je Nixon promenio američki dolar iz dolara podržanog u zlatu u dolar podržan dugom, ovim je promenio i svaku drugu valutu na Zemlji.
Sam je učinio da se celokupna svetska ekonomija zasniva na dugovima. Valute više nisu predstavljale zlato, već su predstavljale vrednost državnog duga.
Zlatni Standard se nikada nije vratio
Konvertibilnost američkih dolara u zlato – zlatni standard – nikada se nije vratio.
Od 1971. godine, čitav globalni monetarni sistem pokreće se tradicionalnim “fiat” valutama: poverenjem u vladine institucije da održavaju valutni sistem.
Većina valuta podržana je kombinacijom duga njihove vlade i drugih tradicionalnih valuta poput dolara i evra. Papirne valute više nisu podržane zlatom, imovinom koja je više od 5000 godina služila kao težak novac.
Danas vas vlade prisiljavaju da plaćate porez u njihovoj valuti i manipulišu saznanjima oko novca kako bi osigurale da potražnja za njihovom valutom ostane velika.
To im omogućava da neprestano štampaju više valuta, da bi je potrošili na vladine projekte, uzrokujući inflaciju cena koja jede i smanjuje bogatstvo i plate.
Američka vlada sada prodaje državne obveznice (dugove), poznate kao obveznice Trezora SAD, eng. US Treasuries, komercijalnim bankama u zamenu za američke dolare.
Vlada koristi te dolare za finansiranje svog budžetskog deficita. Komercijalne banke prodaju mnoge obveznice Trezora SAD, koje su kupile, američkoj centralnoj banci, Federalnim Rezervama.
Federalne rezerve plaćaju komercijalnim bankama sveže štampanim novcem “pomoću računara i upisivanjem količine na račun”, kako je rekao bivši predsednik Fed-a Ben Bernanke.
Ove komercijalne banke često zarađuju samo kupujući obveznice Trezora SAD od države i prodajući ih centralnoj banci. Kupujte nisko, prodajte visoko.
Centralne banke ovaj proces kupovine državnog duga – odnosno pozajmljivanja novca državi – nazivaju operacijama otvorenog tržišta.
Kada centralna banka odjednom kupi velike iznose duga, oni to nazivaju kvantitativnim ublažavanjem. Centralne banke javno najavljuju kupovinu državnog duga, ali vrlo malo ljudi razume šta to zapravo znači.
Euro, jen i svaka druga valuta koja se danas koristi funkcionišu slično kao američki dolar.
Da li će SAD ikada vratiti svoj nacionalni dug? Neobična stvar u vezi sa državnim dugom SAD-a je ta što vlada poseduje štampariju potrebnu za njegovu otplatu.
Kao rezultat toga, kada vlada duguje novac, oni samo pozajme još više novca da bi otplatile taj dug, povećavajući nacionalni dug.
Ako vam ovo zvuči kao Ponzijeva piramidalna šema, to je zato što ona to i jeste – najveća Ponzijeva šema u istoriji. Kao i svaka Ponzijeva šema, nastaviće se sve dok su ljudi koji kupuju Ponzijevu šemu budu uvereni da će im biti plaćeno nazad.
Ako ljudi i nacije prestanu da se zadužuju i koriste američke dolare jer nemaju poverenja u američku vladu ili vide da cena robe raste (tj. dolar postaje sve manje vredan), potražnja za dolarom će opadati, što će izazvati začaranu spiralu.
Ova spirala često završi u hiperinflaciji, kao što smo videli u novijoj istoriji sa Jugoslavijom, Venecuelom, Argentinom, Zimbabveom i mnogim drugim državama.
Ovo je način kako funkcioniše novac na vašem bankovnom računu. Novac svake nacije na svetu pati od istih problema kao i perle i novčanice u pričama o Njutoniji i Kejnslandu.
Kako banke i vlade kradu tvoj novac?
Tokom vekova, stigli smo do monetarnog sistema u kojem banke i vlade mogu da štampaju novu valutu za finansiranje svojih operacija i svojih prijatelja u zločinu, dok kradu bogatstvo svojih građana.
Šta će se desiti sa svetom kada novac bude mogao da štampa svaki narod na planeti?
- Bogatstvo onih koji su blizu pravljenja nove valute se povećava
- Vlada i politički povlašćena klasa ljudi, imaju pristup novoštampanom novcu pre svih ostalih, pa mogu da ga potroše pre nego što cene porastu. Na ovaj efekat pokazao je ekonomista Richard Cantillon sredinom 1700-ih i poznat je kao Cantillonov Efekat.
- Cena robe raste (poznato kao inflacija
- Ne raste sve roba istovremeno u ceni. Roba blizu mesta gde se proizvodi nova valuta – finansijski sektor i vlada – prva raste, i odatle uzrokuje efekt talasa na cene.
- Inflacija se često predstavlja kao promena cene potrošačke korpe, poznata kao Indeks Potrošačkih Cena, eng. Consumer Price Index (CPI). Vlada ima alate za manipulisanje ovim brojem kako bi osigurala da se ona čini niskom i stabilnom, kao što je objašnjeno u našem članku o inflaciji.
- Finansijska imovina često primećuje ogromnu inflaciju, ali bankari to ne nazivaju inflacijom – oni kažu da naša ekonomija cveta! Nakon što su američke Federalne rezerve učetvorostručile ponudu američkih dolara u šest godina nakon finansijske krize 2008. godine, banke koje su dobile te nove dolare, kupile su akcije i obveznice, stvarajući ogroman balon u cenama ove imovine.
- Štednja i životni standard stanovništva se smanjuju
- Plate su jedna od poslednjih “cena” u ekonomiji koja se prilagođava, jer se često povećavaju samo jednom godišnje. U međuvremenu, cene dnevnih potrepština te osobe koja zaradjuje platu neprestano rastu kako novi novac kruži ekonomijom.
- Najviše su pogođeni oni koji žive od plate do plate – a to je 70% Amerikanaca.
- Razlike u prihodima između bogatih i siromašnih se povećavaju, kao što se vidi na grafikonu ispod.

*Koncentracija dohotka na vrhu naglo je porasla od 1970-ih
Zašto i dalje imamo isti monetarni sistem?
Ako ovaj sistem bogate još više obogaćuje, a siromašne još više osiromašuje, dovodeći do političke nestabilnosti, zašto ga onda ne bismo promenili?
Najveći razlog zašto se ništa ne menja je verovatno to što puno toga ne znamo o samom sistemu. Svi svakodnevno koristimo valute svojih vlada, ali većina nas ne razume kako sistem funkcioniše i šta on čini našim društvima.
Obrazovni sistem, mediji i finansijski stručnjaci neprestano nam govore da je monetarni sistem previše komplikovan da bi ga normalni ljudi razumeli. Mnogi od nas se zato i ne trude da pokušaju.
Još nekoliko razloga zašto ovaj sistem nastavlja da opstaje:
- Mnogo je ljudi koji imaju direktnu korist od štampanja novog novca.
- Ti ljudi ne žele nikakve promene i bore se da zadrže tu moć.
- Nacionalne valute su često pogodne
- Kreditne kartice, online bankarstvo i još mnogo toga čine upravljanje nacionalnim valutama i njihovo trošenje lakim i jednostavnim.
- Građani moraju da plaćaju porez u svojoj nacionalnoj valuti
- To stvara potražnju za tom valutom od svih građana, povećavajući njenu vrednost.
- Glavna međunarodna tržišta, poput nafte, denominirana su u dolarima.
- Nafta je potrebna svakoj zemlji na planeti, ali pošto mnogi ne mogu da je proizvode, moraju da je kupuju na međunarodnim berzama. Od 1970-ih na ovim berzama gotovo sva nafta se prodaje za dolare, što stvara potražnju za dolarima. Da bi se odmaknule od ovog sistema, zemlje bi trebale da pronađu novu valutu ili robu za trgovinu naftom, što zahteva vreme i rizike.
- Nije postojala dobra alternativa
- Uz globalnu ekonomiju u realnom vremenu, naš sistem digitalnog bankarstva koji koristi nacionalne valute je pogodan. Transakcija u tvrdom novcu poput zlata bila bi previše nezgrapna za današnji svet. Digitalna valuta pod nazivom Bitcoin, predstavljena 2009. godine, je rastuća alternativa koja nudi čvrst novac koji se kreće brzinom interneta.
Šta je novac, i zašto trebate da brinete?
Novac je alat koji olakšava razmenu dobara. Kao i svako drugo dobro, novac se pridržava zakona ponude i potražnje – povećanje potražnje povećaće njegovu vrednost, a povećanje ponude smanjiće njegovu vrednost.
Na ovaj način novac se ne razlikuje od kuće ili piletine. Međutim, velika prodajnost novca znači da je potražnja za njim uvek velika. Kao rezultat, novac mora biti težak za proizvodnju (a samim tim i ograničen u ponudi) ili će ga onaj ko ga može napraviti, stvoriti toliko, da vremenom više neće služiti kao zaliha vrednosti. Uskoro će izgubiti svoje funkcije kao sredstvo razmene i obračunske jedinice.
Najbolji novac u datoj ekonomiji je onaj koji se najslobodnije kreće – svi ga žele, lako je obaviti transakcije sa njim i koji sa vremenom dobro drži svoju vrednost. Nijedan novac nije savršen u svemu ovome, a neki ističu jednu funkciju novca na štetu drugih.
Iako se istorija ne ponavlja, ona se rimuje, a usponi i padovi monetarnih sistema imaju jasne ritmove. Uspon i pad monetarnog sistema često sledi opšti obrazac koji smo videli u pričama o agri perlama i Kejnslandu: pojavljuje se odredjenji oblik novca koji pomaže ljudima da efikasnije trguju i štede, ali na kraju gubi na vrednosti kada neko shvati kako da ga jeftino stvori u velikoj količini. Međutim, tokom dugog perioda vremena, monetarni sistemi su se poboljšali u sve tri funkcije novca.
Na primer, zlato je tokom vremena dobro služilo kao zaliha vrednosti. Međutim, naša međusobno povezana ekonomija ne bi mogla efikasno da funkcioniše ako bi trebalo da fizičko zlato zamenimo robom i uslugama. Mnogo je lakše kretati se na papirnom i digitalnom novcu, ali istorija nam govori da su vlade i bankari iskoristili ove oblike novca za krađu bogatstva putem inflacije.
Današnji globalni monetarni sistem je vrlo zgodan, a digitalna plaćanja i kreditne kartice olakšavaju trošenje novca. Ovo skriva stalnu inflaciju koja nagriza vrednost svake jedinice novca i dovodi do sve većeg jaza u bogatstvu.
Nadam se da je ovaj članak proširio vaše razumevanje novca i njegove uloge u društvu. Ovo je samo početak svega što treba istražiti o novcu: za kasnije su sačuvane teme o inflaciji, kamatnim stopama, pozajmljivanju, poslovnim ciklusima i još mnogo toga.
Efikasnija Ušteda Novca
Možda se pitate kako zaštititi svoju štednju kada svaki oblik često korišćenog novca i investicija pati od inflacije ponude – koja umanjuje vrednost i prenosi bogatstvo onima koji mogu da stvore novac ili investiciju. Možda se čini da se ništa na planeti danas ne može kvalifikovati kao ‘težak’ novac, ali dve stvari ipak ostaju: zlato i njegov noviji rođak Bitcoin. Obe ove stvari je neverovatno teško proizvesti, a jedna od njih se kreće brzinom interneta i može se čuvati u vašem mozgu.
Ako želite da saznate više o Bitcoin-u kao sredstvu za zaštitu vaše ušteđevine, pročitajte ovde. Ako ste već spremni za kupovinu Bitcoin-a, pogledajte moj vodič za kupovinu Bitcoin-a. Možete početi sa investiranjem sa samo 5 ili 10 €.

Zasluge
Hvala svima koji su pomogli u izradi i uređivanju ove serije o novcu: @ck_SNARKS, @CryptoRothbard, Neil Woodfine, Emil Sandstedt, Taylor Pearson, Parker Lewis, Jason Choi, mojoj porodici i mnogim drugima.
Hvala svima koji su ovo inspirisali i razvili ključne ideje koje su ovde primenjene: Friedrich Hayek, Carl Menger, Ludwig Von Mises, Murray Rothbard, Saifedean Ammous, Dan Held, Pierre Rochard, Stephan Livera, Michael Goldstein, i mnogi drugi.
Molim vas da šerujete! Ako vam je ovaj članak otvorio oči o tome kako funkcioniše naš novac i finansijski sistem, kontaktirajte me ili ostavite komentar!
Ako vam se sviđa moj rad, molim vas da ga podelite sa svojim prijateljima i porodicom. Cilj mi je da svima pružim pogled u ekonomiju i na to kako ona utiče na njihov život.
-
 @ 21335073:a244b1ad
2025-05-21 16:58:36
@ 21335073:a244b1ad
2025-05-21 16:58:36The other day, I had the privilege of sitting down with one of my favorite living artists. Our conversation was so captivating that I felt compelled to share it. I’m leaving his name out for privacy.
Since our last meeting, I’d watched a documentary about his life, one he’d helped create. I told him how much I admired his openness in it. There’s something strange about knowing intimate details of someone’s life when they know so little about yours—it’s almost like I knew him too well for the kind of relationship we have.
He paused, then said quietly, with a shy grin, that watching the documentary made him realize how “odd and eccentric” he is. I laughed and told him he’s probably the sanest person I know. Because he’s lived fully, chasing love, passion, and purpose with hardly any regrets. He’s truly lived.
Today, I turn 44, and I’ll admit I’m a bit eccentric myself. I think I came into the world this way. I’ve made mistakes along the way, but I carry few regrets. Every misstep taught me something. And as I age, I’m not interested in blending in with the world—I’ll probably just lean further into my own brand of “weird.” I want to live life to the brim. The older I get, the more I see that the “normal” folks often seem less grounded than the eccentric artists who dare to live boldly. Life’s too short to just exist, actually live.
I’m not saying to be strange just for the sake of it. But I’ve seen what the crowd celebrates, and I’m not impressed. Forge your own path, even if it feels lonely or unpopular at times.
It’s easy to scroll through the news and feel discouraged. But actually, this is one of the most incredible times to be alive! I wake up every day grateful to be here, now. The future is bursting with possibility—I can feel it.
So, to my fellow weirdos on nostr: stay bold. Keep dreaming, keep pushing, no matter what’s trending. Stay wild enough to believe in a free internet for all. Freedom is radical—hold it tight. Live with the soul of an artist and the grit of a fighter. Thanks for inspiring me and so many others to keep hoping. Thank you all for making the last year of my life so special.
-
 @ 86611181:9fc27ad7
2025-05-23 20:31:44
@ 86611181:9fc27ad7
2025-05-23 20:31:44It's time to secure user data in your identity system This post was also published with the Industry Association of Privacy Professionals.
It seems like every day there is a new report of a major personal data breach. In just the past few months, Neiman Marcus, Ticketmaster, Evolve Bank, TeamViewer, Hubspot, and even the IRS have been affected.
The core issue is that user data is commonly spread across multiple systems that are increasingly difficult to fully secure, including database user tables, data warehouses and unstructured documents.
Most enterprises are already running an incredibly secure and hardened identity system to manage customer login and authorization, commonly referred to as a customer identity access management system. Since identity systems manage customer sign-up and sign-in, they typically contain customer names, email addresses, and phone numbers for multifactor authentication. Commercial CIAMs provide extensive logging, threat detection, availability and patch management.
Identity systems are highly secure and already store customers' personally identifiable information, so it stands to reason enterprises should consider identity systems to manage additional PII fields.
Identity systems are designed to store numerous PII fields and mask the fields for other systems. The Liberty Project developed the protocols that became Security Assertion Markup Language 2.0, the architecture at the core of CIAM systems, 20 years ago, when I was its chief technology officer. SAML 2.0 was built so identity data would be fully secure, and opaque tokens would be shared with other systems. Using tokens instead of actual user data is a core feature of identity software that can be used to fully secure user data across applications.
Most modern identity systems support adding additional customer fields, so it is easy to add new fields like Social Security numbers and physical addresses. Almost like a database, some identity systems even support additional tables and images.
A great feature of identity systems is that they often provide a full suite of user interface components for users to register, login and manage their profile fields. Moving fields like Social Security numbers from your database to your identity system means the identity system can fully manage the process of users entering, viewing and editing the field, and your existing application and database become descoped from managing sensitive data.
With sensitive fields fully isolated in an identity system and its user interface components, the identity system can provide for cumbersome and expensive compliance with standards such as the Health Insurance Portability and Accountability Act for medical data and the Payment Card Industry Data Security Standard for payment data, saving the time and effort to achieve similar compliance in your application.
There are, of course, applications that require sensitive data, such as customer service systems and data warehouses. Identity systems use a data distribution standard called System for Cross-domain Identity Management 2.0 to copy user data to other systems. The SCIM is a great standard to help manage compliance such as "right to be forgotten," because it can automatically delete customer data from other systems when a customer record is deleted from the identity system.
When copying customer data from an identity system to another application, consider anonymizing or masking fields. For example, anonymizing a birthdate into an age range when copying a customer record into a data warehouse can descope the data warehouse from containing personal information.
Most enterprises already run an Application Programming Interface Gateway to manage web services between systems. By combining an API Gateway with the identity system's APIs, it becomes very easy to automatically anonymize and mask customer data fields before they are copied into other systems.
A new set of companies including Baffle, Skyflow, and Piiano have introduced services that combine the governance and field management features of an identity system with extensive field masking. Since these systems do not offer the authentication and authorization features of an identity system, it's important to balance the additional features as they introduce an additional threat surface with PII storage and permissions.
PII sprawl is an increasing liability for companies. The most secure, compliant and flexible central data store to manage PII is the existing CIAM and API Gateway infrastructure that enterprises have already deployed.
Move that customer data into your identity system and lock it down. https://peter.layer3.press/articles/3c6912eb-404a-4630-9fe9-fd1bd23cfa64
-
 @ e0a24c5c:fa44b1e7
2025-05-23 19:21:04
@ e0a24c5c:fa44b1e7
2025-05-23 19:21:04Ralph Boes – Menschenrechtsaktivist, Philosoph
Ralph Boes zeigt in dem Buch auf, wie wir uns von der Übermacht des Parteienwesens, die zur Entmündigung des Volkes führt, befreien können. Er zeigt, dass schon im Grundgesetz selbst höchst gegenläufige, an seinen freiheitlich-demokratischen Idealen bemessen sogar als verfassungswidrig zu bezeichnende Tendenzen wirken. Und dass diese es sind, die heute in seine Zerstörung führen. Er weist aber auch die Ansatzpunkte auf, durch die der Zerstörung des Grundgesetzes wirkungsvoll begegnet werden kann.
Eintritt frei, Spendentopf
Ralph Boes hat u.a. dafür gesorgt, dass die unmäßigen Sanktionen in Hartz IV 2019 vom Bundesverfassungsgericht für menschenrechts- und verfassungswidrig erklärt wurden. Aktuell setzt er sich für eine Ur-Abstimmung des Volkes über seine Verfassung ein.
-
 @ c9badfea:610f861a
2025-05-24 12:55:17
@ c9badfea:610f861a
2025-05-24 12:55:17Before you post a message or article online, let the LLM check if you are leaking any personal information using this prompt:
Analyze the following text to identify any Personally Identifiable Information (PII): <Your Message>Replace
<Your Message>with your textIf no PII is found, continue by modifying your message to detach it from your personality. You can use any of the following prompts (and further modify it if necessary).
Prompt № 1 - Reddit-Style
Convert the message into a casual, Reddit-style post without losing meaning. Split the message into shorter statements with the same overall meaning. Here is the message: <Your Message>Prompt № 2 - Advanced Modifications
``` Apply the following modifications to the message: - Rewrite it in lowercase - Use "u" instead of "you" - Use "akchoaly" instead of "actually" - Use "hav" instead of "have" - Use "tgat" instead of "that" - Use comma instead of period - Use British English grammar
Here is the message:
``` Prompt № 3 - Neutral Tone
Rewrite the message to correct grammar errors, and ensure the tone is neutral and free of emotional language: <Your Message>Prompt № 4 - Cross Translation Technique
Translate the message into Chinese, then translate the resulting Chinese text back into English. Provide only the final English translation. Here is the message: <Your Message>Check the modified message and send it.
ℹ️ You can use dialects to obfuscate your language further. For example, if you are from the US, you can tell the LLM to use British grammar and vice versa.
⚠️ Always verify the results. Don't fully trust an LLM.
-
 @ 0e9491aa:ef2adadf
2025-05-24 16:01:21
@ 0e9491aa:ef2adadf
2025-05-24 16:01:21
@matt_odell don't you even dare not ask about nostr!
— Kukks (Andrew Camilleri) (@MrKukks) May 18, 2021
Nostr first hit my radar spring 2021: created by fellow bitcoiner and friend, fiatjaf, and released to the world as free open source software. I was fortunate to be able to host a conversation with him on Citadel Dispatch in those early days, capturing that moment in history forever. Since then, the protocol has seen explosive viral organic growth as individuals around the world have contributed their time and energy to build out the protocol and the surrounding ecosystem due to the clear need for better communication tools.
nostr is to twitter as bitcoin is to paypal
As an intro to nostr, let us start with a metaphor:
twitter is paypal - a centralized platform plagued by censorship but has the benefit of established network effects
nostr is bitcoin - an open protocol that is censorship resistant and robust but requires an organic adoption phase
Nostr is an open communication protocol that can be used to send messages across a distributed set of relays in a censorship resistant and robust way.
- Anyone can run a relay.
- Anyone can interact with the protocol.
- Relays can choose which messages they want to relay.
- Users are identified by a simple public private key pair that they can generate themselves.Nostr is often compared to twitter since there are nostr clients that emulate twitter functionality and user interface but that is merely one application of the protocol. Nostr is so much more than a mere twitter competitor. Nostr clients and relays can transmit a wide variety of data and clients can choose how to display that information to users. The result is a revolution in communication with implications that are difficult for any of us to truly comprehend.
Similar to bitcoin, nostr is an open and permissionless protocol. No person, company, or government controls it. Anyone can iterate and build on top of nostr without permission. Together, bitcoin and nostr are incredibly complementary freedom tech tools: censorship resistant, permissionless, robust, and interoperable - money and speech protected by code and incentives, not laws.
As censorship throughout the world continues to escalate, freedom tech provides hope for individuals around the world who refuse to accept the status quo. This movement will succeed on the shoulders of those who choose to stand up and contribute. We will build our own path. A brighter path.
My Nostr Public Key: npub1qny3tkh0acurzla8x3zy4nhrjz5zd8l9sy9jys09umwng00manysew95gx
If you found this post helpful support my work with bitcoin.

-
 @ 51bbb15e:b77a2290
2025-05-21 00:24:36
@ 51bbb15e:b77a2290
2025-05-21 00:24:36Yeah, I’m sure everything in the file is legit. 👍 Let’s review the guard witness testimony…Oh wait, they weren’t at their posts despite 24/7 survellience instructions after another Epstein “suicide” attempt two weeks earlier. Well, at least the video of the suicide is in the file? Oh wait, a techical glitch. Damn those coincidences!
At this point, the Trump administration has zero credibility with me on anything related to the Epstein case and his clients. I still suspect the administration is using the Epstein files as leverage to keep a lot of RINOs in line, whereas they’d be sabotaging his agenda at every turn otherwise. However, I just don’t believe in ends-justify-the-means thinking. It’s led almost all of DC to toss out every bit of the values they might once have had.
-
 @ 95cbd62b:a5270126
2025-05-24 14:06:33
@ 95cbd62b:a5270126
2025-05-24 14:06:33Trong thời đại công nghệ số phát triển mạnh mẽ, nhu cầu tìm kiếm một nền tảng tích hợp đầy đủ tiện ích, an toàn và thân thiện với người dùng ngày càng tăng cao. OK22 đã chứng minh vị thế của mình không chỉ là một nền tảng giải trí trực tuyến, mà còn là một công cụ công nghệ thông minh phục vụ mọi nhu cầu trong đời sống số. Với thiết kế giao diện 100% tiếng Việt và khả năng tương thích trên mọi thiết bị từ máy tính đến điện thoại, OK22 mang đến cho người dùng trải nghiệm mượt mà, dễ sử dụng và hoàn toàn bảo mật. Được phát triển trên nền tảng công nghệ hiện đại, OK22 hỗ trợ người dùng quản lý thông tin cá nhân, thực hiện giao dịch nhanh chóng, lưu trữ dữ liệu an toàn và tiếp cận các tiện ích công nghệ tiên tiến một cách dễ dàng, kể cả với người mới sử dụng.
Một trong những điểm mạnh nổi bật của OK22 chính là khả năng tự động hóa trong xử lý tác vụ, giúp tiết kiệm thời gian và tối ưu hóa hiệu suất làm việc. Nền tảng được trang bị hệ thống bảo mật cao cấp, bảo vệ tối đa quyền riêng tư và tài sản số của người dùng. OK22 còn cung cấp hệ thống hỗ trợ trực tuyến 24/7, giúp người dùng giải quyết mọi vấn đề nhanh chóng mà không bị gián đoạn. Dù là một cá nhân đang tìm kiếm công cụ quản lý tài chính cá nhân, một doanh nghiệp nhỏ cần nền tảng để xử lý đơn hàng và thanh toán, hay một nhóm cộng đồng cần không gian kết nối số – OK22 đều có thể đáp ứng linh hoạt và hiệu quả. Không những vậy, nhờ tích hợp nhiều tính năng như thông báo tự động, đồng bộ dữ liệu đám mây, và tích hợp API mở, OK22 còn dễ dàng kết nối với các nền tảng khác trong hệ sinh thái số, giúp người dùng tạo nên một môi trường làm việc và sinh hoạt thông minh.
Không dừng lại ở đó, OK22 đang ngày càng mở rộng hợp tác với các đối tác lớn trong nhiều lĩnh vực như giáo dục trực tuyến, thương mại điện tử, chăm sóc sức khỏe và tài chính cá nhân. Nền tảng không ngừng cập nhật những công nghệ tiên tiến như AI, blockchain và dữ liệu lớn (Big Data) nhằm mang lại trải nghiệm người dùng tối ưu và đáp ứng nhu cầu ngày càng đa dạng của cộng đồng Việt. Với tốc độ xử lý nhanh, giao diện trực quan và độ tin cậy cao, OK22 không chỉ đơn thuần là một ứng dụng công nghệ – mà còn là người bạn đồng hành tin cậy trong hành trình số hóa của người Việt. Trong tương lai gần, OK22 hứa hẹn sẽ trở thành nền tảng công nghệ không thể thiếu trong mỗi gia đình, tổ chức và doanh nghiệp, đóng vai trò then chốt trong việc thúc đẩy chuyển đổi số toàn diện và phát triển bền vững.
-
 @ 56f27915:5fee3024
2025-05-23 18:51:08
@ 56f27915:5fee3024
2025-05-23 18:51:08Ralph Boes – Menschenrechtsaktivist, Philosoph, Vorstandsmitglied im Verein Unsere Verfassung e.V.
Ralph Boes zeigt in dem Buch auf, wie wir uns von der Übermacht des Parteienwesens, die zur Entmündigung des Volkes führt, befreien können. Er zeigt, dass schon im Grundgesetz selbst höchst gegenläufige, an seinen freiheitlich-demokratischen Idealen bemessen sogar als verfassungswidrig zu bezeichnende Tendenzen wirken. Und dass diese es sind, die heute in seine Zerstörung führen. Er weist aber auch die Ansatzpunkte auf, durch die der Zerstörung des Grundgesetzes wirkungsvoll begegnet werden kann.
Eintritt frei, Spendentopf
Ralph Boes hat u.a. dafür gesorgt, dass die unmäßigen Sanktionen in Hartz IV 2019 vom Bundesverfassungsgericht für menschenrechts- und verfassungswidrig erklärt wurden. Aktuell setzt er sich für eine Ur-Abstimmung des Volkes über seine Verfassung ein.
-
 @ c9badfea:610f861a
2025-05-20 19:49:20
@ c9badfea:610f861a
2025-05-20 19:49:20- Install Sky Map (it's free and open source)
- Launch the app and tap Accept, then tap OK
- When asked to access the device's location, tap While Using The App
- Tap somewhere on the screen to activate the menu, then tap ⁝ and select Settings
- Disable Send Usage Statistics
- Return to the main screen and enjoy stargazing!
ℹ️ Use the 🔍 icon in the upper toolbar to search for a specific celestial body, or tap the 👁️ icon to activate night mode
-
 @ 3bf0c63f:aefa459d
2024-12-06 20:37:26
@ 3bf0c63f:aefa459d
2024-12-06 20:37:26início
"Vocês vêem? Vêem a história? Vêem alguma coisa? Me parece que estou tentando lhes contar um sonho -- fazendo uma tentativa inútil, porque nenhum relato de sonho pode transmitir a sensação de sonho, aquela mistura de absurdo, surpresa e espanto numa excitação de revolta tentando se impôr, aquela noção de ser tomado pelo incompreensível que é da própria essência dos sonhos..."
Ele ficou em silêncio por alguns instantes.
"... Não, é impossível; é impossível transmitir a sensação viva de qualquer época determinada de nossa existência -- aquela que constitui a sua verdade, o seu significado, a sua essência sutil e contundente. É impossível. Vivemos, como sonhamos -- sozinhos..."
- Livros mencionados por Olavo de Carvalho
- Antiga homepage Olavo de Carvalho
- Bitcoin explicado de um jeito correto e inteligível
- Reclamações
-
 @ 3bf0c63f:aefa459d
2024-10-31 16:08:50
@ 3bf0c63f:aefa459d
2024-10-31 16:08:50Anglicismos estúpidos no português contemporâneo
Palavras e expressões que ninguém deveria usar porque não têm o sentido que as pessoas acham que têm, são apenas aportuguesamentos de palavras inglesas que por nuances da história têm um sentido ligeiramente diferente em inglês.
Cada erro é acompanhado também de uma sugestão de como corrigi-lo.
Palavras que existem em português com sentido diferente
- submissão (de trabalhos): envio, apresentação
- disrupção: perturbação
- assumir: considerar, pressupor, presumir
- realizar: perceber
- endereçar: tratar de
- suporte (ao cliente): atendimento
- suportar (uma idéia, um projeto): apoiar, financiar
- suportar (uma função, recurso, característica): oferecer, ser compatível com
- literacia: instrução, alfabetização
- convoluto: complicado.
- acurácia: precisão.
- resiliência: resistência.
Aportuguesamentos desnecessários
- estartar: iniciar, começar
- treidar: negociar, especular
Expressões
- "não é sobre...": "não se trata de..."

Ver também
-
 @ 3bf0c63f:aefa459d
2024-09-18 10:37:09
@ 3bf0c63f:aefa459d
2024-09-18 10:37:09How to do curation and businesses on Nostr
Suppose you want to start a Nostr business.
You might be tempted to make a closed platform that reuses Nostr identities and grabs (some) content from the external Nostr network, only to imprison it inside your thing -- and then you're going to run an amazing AI-powered algorithm on that content and "surface" only the best stuff and people will flock to your app.
This will be specially good if you're going after one of the many unexplored niches of Nostr in which reading immediately from people you know doesn't work as you generally want to discover new things from the outer world, such as:
- food recipe sharing;
- sharing of long articles about varying topics;
- markets for used goods;
- freelancer work and job offers;
- specific in-game lobbies and matchmaking;
- directories of accredited professionals;
- sharing of original music, drawings and other artistic creations;
- restaurant recommendations
- and so on.
But that is not the correct approach and damages the freedom and interoperability of Nostr, posing a centralization threat to the protocol. Even if it "works" and your business is incredibly successful it will just enshrine you as the head of a platform that controls users and thus is prone to all the bad things that happen to all these platforms. Your company will start to display ads and shape the public discourse, you'll need a big legal team, the FBI will talk to you, advertisers will play a big role and so on.
If you are interested in Nostr today that must be because you appreciate the fact that it is not owned by any companies, so it's safe to assume you don't want to be that company that owns it. So what should you do instead? Here's an idea in two steps:
- Write a Nostr client tailored to the niche you want to cover
If it's a music sharing thing, then the client will have a way to play the audio and so on; if it's a restaurant sharing it will have maps with the locations of the restaurants or whatever, you get the idea. Hopefully there will be a NIP or a NUD specifying how to create and interact with events relating to this niche, or you will write or contribute with the creation of one, because without interoperability this can't be Nostr.
The client should work independently of any special backend requirements and ideally be open-source. It should have a way for users to configure to which relays they want to connect to see "global" content -- i.e., they might want to connect to
wss://nostr.chrysalisrecords.com/to see only the latest music releases accredited by that label or towss://nostr.indiemusic.com/to get music from independent producers from that community.- Run a relay that does all the magic
This is where your value-adding capabilities come into play: if you have that magic sauce you should be able to apply it here. Your service -- let's call it
wss://magicsaucemusic.com/-- will charge people or do some KYM (know your music) validation or use some very advanced AI sorcery to filter out the spam and the garbage and display the best content to your users who will request the global feed from it (["REQ", "_", {}]), and this will cause people to want to publish to your relay while others will want to read from it.You set your relay as the default option in the client and let things happen. Your relay is like your "website" and people are free to connect to it or not. You don't own the network, you're just competing against other websites on a leveled playing field, so you're not responsible for it. Users get seamless browsing across multiple websites, unified identities, a unified interface (that could be different in a different client) and social interaction capabilities that work in the same way for all, and they do not depend on you, therefore they're more likely to trust you.
Does this centralize the network still? But this a simple and easy way to go about the matter and scales well in all aspects.
Besides allowing users to connect to specific relays for getting a feed of curated content, such clients should also do all kinds of "social" (i.e. following, commenting etc) activities (if they choose to do that) using the outbox model -- i.e. if I find a musician I like under
wss://magicsaucemusic.comand I decide to follow them I should keep getting updates from them even if they get banned from that relay and start publishing onwss://nos.lolorwss://relay.damus.ioor whatever relay that doesn't even know anything about music.The hardcoded defaults and manual typing of relay URLs can be annoying. But I think it works well at the current stage of Nostr development. Soon, though, we can create events that recommend other relays or share relay lists specific to each kind of activity so users can get in-app suggestions of relays their friends are using to get their music from and so on. That kind of stuff can go a long way.
-
 @ 08f96856:ffe59a09
2025-05-15 01:22:34
@ 08f96856:ffe59a09
2025-05-15 01:22:34เมื่อพูดถึง Bitcoin Standard หลายคนมักนึกถึงภาพโลกอนาคตที่ทุกคนใช้บิตคอยน์ซื้อกาแฟหรือของใช้ในชีวิตประจำวัน ภาพแบบนั้นดูเหมือนไกลตัวและเป็นไปไม่ได้ในความเป็นจริง หลายคนถึงกับพูดว่า “คงไม่ทันเห็นในช่วงชีวิตนี้หรอก” แต่ในมุมมองของผม Bitcoin Standard อาจไม่ได้เริ่มต้นจากการที่เราจ่ายบิตคอยน์โดยตรงในร้านค้า แต่อาจเริ่มจากบางสิ่งที่เงียบกว่า ลึกกว่า และเกิดขึ้นแล้วในขณะนี้ นั่นคือ การล่มสลายทีละน้อยของระบบเฟียตที่เราใช้กันอยู่
ระบบเงินที่อิงกับอำนาจรัฐกำลังเข้าสู่ช่วงขาลง รัฐบาลทั่วโลกกำลังจมอยู่ในภาระหนี้ระดับประวัติการณ์ แม้แต่ประเทศมหาอำนาจก็เริ่มแสดงสัญญาณของภาวะเสี่ยงผิดนัดชำระหนี้ อัตราเงินเฟ้อกลายเป็นปัญหาเรื้อรังที่ไม่มีท่าทีจะหายไป ธนาคารที่เคยโอนฟรีเริ่มกลับมาคิดค่าธรรมเนียม และประชาชนก็เริ่มรู้สึกถึงการเสื่อมศรัทธาในระบบการเงินดั้งเดิม แม้จะยังพูดกันไม่เต็มเสียงก็ตาม
ในขณะเดียวกัน บิตคอยน์เองก็กำลังพัฒนาแบบเงียบ ๆ เงียบ... แต่ไม่เคยหยุด โดยเฉพาะในระดับ Layer 2 ที่เริ่มแสดงศักยภาพอย่างจริงจัง Lightning Network เป็น Layer 2 ที่เปิดใช้งานมาได้ระยะเวลสหนึ่ง และยังคงมีบทบาทสำคัญที่สุดในระบบนิเวศของบิตคอยน์ มันทำให้การชำระเงินเร็วขึ้น มีต้นทุนต่ำ และไม่ต้องบันทึกทุกธุรกรรมลงบล็อกเชน เครือข่ายนี้กำลังขยายตัวทั้งในแง่ของโหนดและการใช้งานจริงทั่วโลก
ขณะเดียวกัน Layer 2 ทางเลือกอื่นอย่าง Ark Protocol ก็กำลังพัฒนาเพื่อตอบโจทย์ด้านความเป็นส่วนตัวและประสบการณ์ใช้งานที่ง่าย BitVM เปิดแนวทางใหม่ให้บิตคอยน์รองรับ smart contract ได้ในระดับ Turing-complete ซึ่งทำให้เกิดความเป็นไปได้ในกรณีใช้งานอีกมากมาย และเทคโนโลยีที่น่าสนใจอย่าง Taproot Assets, Cashu และ Fedimint ก็ทำให้การออกโทเคนหรือสกุลเงินที่อิงกับบิตคอยน์เป็นจริงได้บนโครงสร้างของบิตคอยน์เอง
เทคโนโลยีเหล่านี้ไม่ใช่การเติบโตแบบปาฏิหาริย์ แต่มันคืบหน้าอย่างต่อเนื่องและมั่นคง และนั่นคือเหตุผลที่มันจะ “อยู่รอด” ได้ในระยะยาว เมื่อฐานของความน่าเชื่อถือไม่ใช่บริษัท รัฐบาล หรือทุน แต่คือสิ่งที่ตรวจสอบได้และเปลี่ยนกฎไม่ได้
แน่นอนว่าบิตคอยน์ต้องแข่งขันกับ stable coin, เงินดิจิทัลของรัฐ และ cryptocurrency อื่น ๆ แต่สิ่งที่ทำให้มันเหนือกว่านั้นไม่ใช่ฟีเจอร์ หากแต่เป็นความทนทาน และความมั่นคงของกฎที่ไม่มีใครเปลี่ยนได้ ไม่มีทีมพัฒนา ไม่มีบริษัท ไม่มีประตูปิด หรือการยึดบัญชี มันยืนอยู่บนคณิตศาสตร์ พลังงาน และเวลา
หลายกรณีใช้งานที่เคยถูกทดลองในโลกคริปโตจะค่อย ๆ เคลื่อนเข้ามาสู่บิตคอยน์ เพราะโครงสร้างของมันแข็งแกร่งกว่า ไม่ต้องการทีมพัฒนาแกนกลาง ไม่ต้องพึ่งกลไกเสี่ยงต่อการผูกขาด และไม่ต้องการ “ความเชื่อใจ” จากใครเลย
Bitcoin Standard ที่ผมพูดถึงจึงไม่ใช่การเปลี่ยนแปลงแบบพลิกหน้ามือเป็นหลังมือ แต่คือการ “เปลี่ยนฐานของระบบ” ทีละชั้น ระบบการเงินใหม่ที่อิงอยู่กับบิตคอยน์กำลังเกิดขึ้นแล้ว มันไม่ใช่โลกที่ทุกคนถือเหรียญบิตคอยน์ แต่มันคือโลกที่คนใช้อาจไม่รู้ตัวด้วยซ้ำว่า “สิ่งที่เขาใช้นั้นอิงอยู่กับบิตคอยน์”
ผู้คนอาจใช้เงินดิจิทัลที่สร้างบน Layer 3 หรือ Layer 4 ผ่านแอป ผ่านแพลตฟอร์ม หรือผ่านสกุลเงินใหม่ที่ดูไม่ต่างจากเดิม แต่เบื้องหลังของระบบจะผูกไว้กับบิตคอยน์
และถ้ามองในเชิงพัฒนาการ บิตคอยน์ก็เหมือนกับอินเทอร์เน็ต ครั้งหนึ่งอินเทอร์เน็ตก็ถูกมองว่าเข้าใจยาก ต้องพิมพ์ http ต้องรู้จัก TCP/IP ต้องตั้ง proxy เอง แต่ปัจจุบันผู้คนใช้งานอินเทอร์เน็ตโดยไม่รู้ว่าเบื้องหลังมีอะไรเลย บิตคอยน์กำลังเดินตามเส้นทางเดียวกัน โปรโตคอลกำลังถอยออกจากสายตา และวันหนึ่งเราจะ “ใช้มัน” โดยไม่ต้องรู้ว่ามันคืออะไร
หากนับจากช่วงเริ่มต้นของอินเทอร์เน็ตในยุค 1990 จนกลายเป็นโครงสร้างหลักของโลกในสองทศวรรษ เส้นเวลาของบิตคอยน์ก็กำลังเดินตามรอยเท้าของอินเทอร์เน็ต และถ้าเราเชื่อว่าวัฏจักรของเทคโนโลยีมีจังหวะของมันเอง เราก็จะรู้ว่า Bitcoin Standard นั้นไม่ใช่เรื่องของอนาคตไกลโพ้น แต่มันเกิดขึ้นแล้ว
siamstr
-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 3f770d65:7a745b24
2025-04-21 00:15:06
@ 3f770d65:7a745b24
2025-04-21 00:15:06At the recent Launch Music Festival and Conference in Lancaster, PA, featuring over 120 musicians across three days, I volunteered my time with Tunestr and Phantom Power Music's initiative to introduce artists to Bitcoin, Nostr, and the value-for-value model. Tunestr sponsored a stage, live-streaming 21 bands to platforms like Tunestr.io, Fountain.fm and other Nostr/Podcasting 2.0 apps and on-boarding as many others as possible at our conference booth. You may have seen me spamming about this over the last few days.
V4V Earnings
Day 1: 180,000 sats
Day 2: 300,000 sats
Day 3: Over 500,000 sats
Who?
Here are the artists that were on-boarded to Fountain and were live streaming on the Value-for-Value stage:
nostr:npub1cruu4z0hwg7n3r2k7262vx8jsmra3xpku85frl5fnfvrwz7rd7mq7e403w nostr:npub12xeh3n7w8700z4tpd6xlhlvg4vtg4pvpxd584ll5sva539tutc3q0tn3tz nostr:npub1rc80p4v60uzfhvdgxemhvcqnzdj7t59xujxdy0lcjxml3uwdezyqtrpe0j @npub16vxr4pc2ww3yaez9q4s53zkejjfd0djs9lfe55sjhnqkh nostr:npub10uspdzg4fl7md95mqnjszxx82ckdly8ezac0t3s06a0gsf4f3lys8ypeak nostr:npub1gnyzexr40qut0za2c4a0x27p4e3qc22wekhcw3uvdx8mwa3pen0s9z90wk nostr:npub13qrrw2h4z52m7jh0spefrwtysl4psfkfv6j4j672se5hkhvtyw7qu0almy nostr:npub1p0kuqxxw2mxczc90vcurvfq7ljuw2394kkqk6gqnn2cq0y9eq5nq87jtkk nostr:npub182kq0sdp7chm67uq58cf4vvl3lk37z8mm5k5067xe09fqqaaxjsqlcazej nostr:npub162hr8kd96vxlanvggl08hmyy37qsn8ehgj7za7squl83um56epnswkr399 nostr:npub17jzk5ex2rafres09c4dnn5mm00eejye6nrurnlla6yn22zcpl7vqg6vhvx nostr:npub176rnksulheuanfx8y8cr2mrth4lh33svvpztggjjm6j2pqw6m56sq7s9vz nostr:npub1akv7t7xpalhsc4nseljs0c886jzuhq8u42qdcwvu972f3mme9tjsgp5xxk nostr:npub18x0gv872489lrczp9d9m4hx59r754x7p9rg2jkgvt7ul3kuqewtqsssn24
Many more musicians were on-boarded to Fountain, however, we were unable to obtain all of their npubs.
THANK YOU TO ALL ZAPPERS AND BOOSTERS!
Musicians “Get It”
My key takeaway was the musicians' absolute understanding that the current digital landscape along with legacy social media is failing them. Every artist I spoke with recognized how algorithms hinder fan connection and how gatekeepers prevent fair compensation for their work. They all use Spotify, but they only do so out of necessity. They felt the music industry is primed for both a social and monetary revolution. Some of them were even speaking my language…
Because of this, concepts like decentralization, censorship resistance, owning your content, and controlling your social graph weren't just understood by them, they were instantly embraced. The excitement was real; they immediately saw the potential and agreed with me. Bitcoin and Nostr felt genuinely punk rock and that helped a lot of them identify with what we were offering them.
The Tools and the Issues
While the Nostr ecosystem offers a wide variety of tools, we focused on introducing three key applications at this event to keep things clear for newcomers:
- Fountain, with a music focus, was the primary tool for onboarding attendees onto Nostr. Fountain was also chosen thanks to Fountain’s built-in Lightning wallet.
- Primal, as a social alternative, was demonstrated to show how users can take their Nostr identity and content seamlessly between different applications.
- Tunestr.io, lastly was showcased for its live video streaming capabilities.
Although we highlighted these three, we did inform attendees about the broader range of available apps and pointed them to
nostrapps.comif they wanted to explore further, aiming to educate without overwhelming them.This review highlights several UX issues with the Fountain app, particularly concerning profile updates, wallet functionality, and user discovery. While Fountain does work well, these minor hiccups make it extremely hard for on-boarding and education.
- Profile Issues:
- When a user edits their profile (e.g., Username/Nostr address, Lightning address) either during or after creation, the changes don't appear to consistently update across the app or sync correctly with Nostr relays.
- Specifically, the main profile display continues to show the old default Username/Nostr address and Lightning address inside Fountain and on other Nostr clients.
- However, the updated Username/Nostr address does appear on https://fountain.fm (chosen-username@fountain.fm) and is visible within the "Edit Profile" screen itself in the app.
- This inconsistency is confusing for users, as they see their updated information in some places but not on their main public-facing profile within the app. I confirmed this by observing a new user sign up and edit their username – the edit screen showed the new name, but the profile display in Fountain did not update and we did not see it inside Primal, Damus, Amethyst, etc.
- Wallet Limitations:
- The app's built-in wallet cannot scan Lightning address QR codes to initiate payments.
- This caused problems during the event where users imported Bitcoin from Azte.co vouchers into their Fountain wallets. When they tried to Zap a band by scanning a QR code on the live tally board, Fountain displayed an error message stating the invoice or QR code was invalid.
- While suggesting musicians install Primal as a second Nostr app was a potential fix for the QR code issue, (and I mentioned it to some), the burden of onboarding users onto two separate applications, potentially managing two different wallets, and explaining which one works for specific tasks creates a confusing and frustrating user experience.
- Search Difficulties:
- Finding other users within the Fountain app is challenging. I was unable to find profiles from brand new users by entering their chosen Fountain username.
- To find a new user, I had to resort to visiting their profile on the web (fountain.fm/username) to retrieve their npub. Then, open Primal and follow them. Finally, when searching for their username, since I was now following them, I was able to find their profile.
- This search issue is compounded by the profile syncing problem mentioned earlier, as even if found via other clients, their displayed information is outdated.
- Searching for the event to Boost/Zap inside Fountain was harder than it should have been the first two days as the live stream did not appear at the top of the screen inside the tap. This was resolved on the third day of the event.
Improving the Onboarding Experience
To better support user growth, educators and on-boarders need more feature complete and user-friendly applications. I love our developers and I will always sing their praises from the highest mountain tops, however I also recognize that the current tools present challenges that hinder a smooth onboarding experience.
One potential approach explored was guiding users to use Primal (including its built-in wallet) in conjunction with Wavlake via Nostr Wallet Connect (NWC). While this could facilitate certain functions like music streaming, zaps, and QR code scanning (which require both Primal and Wavlake apps), Wavlake itself has usability issues. These include inconsistent or separate profiles between web and mobile apps, persistent "Login" buttons even when logged in on the mobile app with a Nostr identity, and the minor inconvenience of needing two separate applications. Although NWC setup is relatively easy and helps streamline the process, the need to switch between apps adds complexity, especially when time is limited and we’re aiming to showcase the benefits of this new system.
Ultimately, we need applications that are more feature-complete and intuitive for mainstream users to improve the onboarding experience significantly.
Looking forward to the future
I anticipate that most of these issues will be resolved when these applications address them in the near future. Specifically, this would involve Fountain fixing its profile issues and integrating Nostr Wallet Connect (NWC) to allow users to utilize their Primal wallet, or by enabling the scanning of QR codes that pay out to Lightning addresses. Alternatively, if Wavlake resolves the consistency problems mentioned earlier, this would also significantly improve the situation giving us two viable solutions for musicians.
My ideal onboarding event experience would involve having all the previously mentioned issues resolved. Additionally, I would love to see every attendee receive a $5 or $10 voucher to help them start engaging with value-for-value, rather than just the limited number we distributed recently. The goal is to have everyone actively zapping and sending Bitcoin throughout the event. Maybe we can find a large sponsor to facilitate this in the future?
What's particularly exciting is the Launch conference's strong interest in integrating value-for-value across their entire program for all musicians and speakers at their next event in Dallas, Texas, coming later this fall. This presents a significant opportunity to onboard over 100+ musicians to Bitcoin and Nostr, which in turn will help onboard their fans and supporters.
We need significantly more zaps and more zappers! It's unreasonable to expect the same dedicated individuals to continuously support new users; they are being bled dry. A shift is needed towards more people using bitcoin for everyday transactions, treating it as money. This brings me back to my ideal onboarding experience: securing a sponsor to essentially give participants bitcoin funds specifically for zapping and tipping artists. This method serves as a practical lesson in using bitcoin as money and showcases the value-for-value principle from the outset.
-
 @ 5144fe88:9587d5af
2025-05-23 17:01:37
@ 5144fe88:9587d5af
2025-05-23 17:01:37The recent anomalies in the financial market and the frequent occurrence of world trade wars and hot wars have caused the world's political and economic landscape to fluctuate violently. It always feels like the financial crisis is getting closer and closer.
This is a systematic analysis of the possibility of the current global financial crisis by Manus based on Ray Dalio's latest views, US and Japanese economic and financial data, Buffett's investment behavior, and historical financial crises.
Research shows that the current financial system has many preconditions for a crisis, especially debt levels, market valuations, and investor behavior, which show obvious crisis signals. The probability of a financial crisis in the short term (within 6-12 months) is 30%-40%,
in the medium term (within 1-2 years) is 50%-60%,
in the long term (within 2-3 years) is 60%-70%.
Japan's role as the world's largest holder of overseas assets and the largest creditor of the United States is particularly critical. The sharp appreciation of the yen may be a signal of the return of global safe-haven funds, which will become an important precursor to the outbreak of a financial crisis.
Potential conditions for triggering a financial crisis Conditions that have been met 1. High debt levels: The debt-to-GDP ratio of the United States and Japan has reached a record high. 2. Market overvaluation: The ratio of stock market to GDP hits a record high 3. Abnormal investor behavior: Buffett's cash holdings hit a record high, with net selling for 10 consecutive quarters 4. Monetary policy shift: Japan ends negative interest rates, and the Fed ends the rate hike cycle 5. Market concentration is too high: a few technology stocks dominate market performance
Potential trigger points 1. The Bank of Japan further tightens monetary policy, leading to a sharp appreciation of the yen and the return of overseas funds 2. The US debt crisis worsens, and the proportion of interest expenses continues to rise to unsustainable levels 3. The bursting of the technology bubble leads to a collapse in market confidence 4. The trade war further escalates, disrupting global supply chains and economic growth 5. Japan, as the largest creditor of the United States, reduces its holdings of US debt, causing US debt yields to soar
Analysis of the similarities and differences between the current economic environment and the historical financial crisis Debt level comparison Current debt situation • US government debt to GDP ratio: 124.0% (December 2024) • Japanese government debt to GDP ratio: 216.2% (December 2024), historical high 225.8% (March 2021) • US total debt: 36.21 trillion US dollars (May 2025) • Japanese debt/GDP ratio: more than 250%-263% (Japanese Prime Minister’s statement)
Before the 2008 financial crisis • US government debt to GDP ratio: about 64% (2007) • Japanese government debt to GDP ratio: about 175% (2007)
Before the Internet bubble in 2000 • US government debt to GDP ratio: about 55% (1999) • Japanese government debt to GDP ratio: about 130% (1999)
Key differences • The current US debt-to-GDP ratio is nearly twice that before the 2008 crisis • The current Japanese debt-to-GDP ratio is more than 1.2 times that before the 2008 crisis • Global debt levels are generally higher than historical pre-crisis levels • US interest payments are expected to devour 30% of fiscal revenue (Moody's warning)
Monetary policy and interest rate environment
Current situation • US 10-year Treasury yield: about 4.6% (May 2025) • Bank of Japan policy: end negative interest rates and start a rate hike cycle • Bank of Japan's holdings of government bonds: 52%, plans to reduce purchases to 3 trillion yen per month by January-March 2026 • Fed policy: end the rate hike cycle and prepare to cut interest rates
Before the 2008 financial crisis • US 10-year Treasury yield: about 4.5%-5% (2007) • Fed policy: continuous rate hikes from 2004 to 2006, and rate cuts began in 2007 • Bank of Japan policy: maintain ultra-low interest rates
Key differences • Current US interest rates are similar to those before the 2008 crisis, but debt levels are much higher than then • Japan is in the early stages of ending its loose monetary policy, unlike before historical crises • The size of global central bank balance sheets is far greater than at any time in history
Market valuations and investor behavior Current situation • The ratio of stock market value to the size of the US economy: a record high • Buffett's cash holdings: $347 billion (28% of assets), a record high • Market concentration: US stock growth mainly relies on a few technology giants • Investor sentiment: Technology stocks are enthusiastic, but institutional investors are beginning to be cautious
Before the 2008 financial crisis • Buffett's cash holdings: 25% of assets (2005) • Market concentration: Financial and real estate-related stocks performed strongly • Investor sentiment: The real estate market was overheated and subprime products were widely popular
Before the 2000 Internet bubble • Buffett's cash holdings: increased from 1% to 13% (1998) • Market concentration: Internet stocks were extremely highly valued • Investor sentiment: Tech stocks are in a frenzy
Key differences • Buffett's current cash holdings exceed any pre-crisis level in history • Market valuation indicators have reached a record high, exceeding the levels before the 2000 bubble and the 2008 crisis • The current market concentration is higher than any period in history, and a few technology stocks dominate market performance
Safe-haven fund flows and international relations Current situation • The status of the yen: As a safe-haven currency, the appreciation of the yen may indicate a rise in global risk aversion • Trade relations: The United States has imposed tariffs on Japan, which is expected to reduce Japan's GDP growth by 0.3 percentage points in fiscal 2025 • International debt: Japan is one of the largest creditors of the United States
Before historical crises • Before the 2008 crisis: International capital flows to US real estate and financial products • Before the 2000 bubble: International capital flows to US technology stocks
Key differences • Current trade frictions have intensified and the trend of globalization has weakened • Japan's role as the world's largest holder of overseas assets has become more prominent • International debt dependence is higher than any period in history
-
 @ 3f770d65:7a745b24
2025-01-19 21:48:49
@ 3f770d65:7a745b24
2025-01-19 21:48:49The recent shutdown of TikTok in the United States due to a potential government ban serves as a stark reminder how fragile centralized platforms truly are under the surface. While these platforms offer convenience, a more polished user experience, and connectivity, they are ultimately beholden to governments, corporations, and other authorities. This makes them vulnerable to censorship, regulation, and outright bans. In contrast, Nostr represents a shift in how we approach online communication and content sharing. Built on the principles of decentralization and user choice, Nostr cannot be banned, because it is not a platform—it is a protocol.
PROTOCOLS, NOT PLATFORMS.
At the heart of Nostr's philosophy is user choice, a feature that fundamentally sets it apart from legacy platforms. In centralized systems, the user experience is dictated by a single person or governing entity. If the platform decides to filter, censor, or ban specific users or content, individuals are left with little action to rectify the situation. They must either accept the changes or abandon the platform entirely, often at the cost of losing their social connections, their data, and their identity.
What's happening with TikTok could never happen on Nostr. With Nostr, the dynamics are completely different. Because it is a protocol, not a platform, no single entity controls the ecosystem. Instead, the protocol enables a network of applications and relays that users can freely choose from. If a particular application or relay implements policies that a user disagrees with, such as censorship, filtering, or even government enforced banning, they are not trapped or abandoned. They have the freedom to move to another application or relay with minimal effort.
THIS IS POWERFUL.
Take, for example, the case of a relay that decides to censor specific content. On a legacy platform, this would result in frustration and a loss of access for users. On Nostr, however, users can simply connect to a different relay that does not impose such restrictions. Similarly, if an application introduces features or policies that users dislike, they can migrate to a different application that better suits their preferences, all while retaining their identity and social connections.
The same principles apply to government bans and censorship. A government can ban a specific application or even multiple applications, just as it can block one relay or several relays. China has implemented both tactics, yet Chinese users continue to exist and actively participate on Nostr, demonstrating Nostr's ability to resistant censorship.
How? Simply, it turns into a game of whack-a-mole. When one relay is censored, another quickly takes its place. When one application is banned, another emerges. Users can also bypass these obstacles by running their own relays and applications directly from their homes or personal devices, eliminating reliance on larger entities or organizations and ensuring continuous access.
AGAIN, THIS IS POWERUFL.
Nostr's open and decentralized design makes it resistant to the kinds of government intervention that led to TikTok's outages this weekend and potential future ban in the next 90 days. There is no central server to target, no company to regulate, and no single point of failure. (Insert your CEO jokes here). As long as there are individuals running relays and applications, users continue creating notes and sending zaps.
Platforms like TikTok can be silenced with the stroke of a pen, leaving millions of users disconnected and abandoned. Social communication should not be silenced so incredibly easily. No one should have that much power over social interactions.
Will we on-board a massive wave of TikTokers in the coming hours or days? I don't know.
TikTokers may not be ready for Nostr yet, and honestly, Nostr may not be ready for them either. The ecosystem still lacks the completely polished applications, tools, and services they’re accustomed to. This is where we say "we're still early". They may not be early adopters like the current Nostr user base. Until we bridge that gap, they’ll likely move to the next centralized platform, only to face another government ban or round of censorship in the future. But eventually, there will come a tipping point, a moment when they’ve had enough. When that time comes, I hope we’re prepared. If we’re not, we risk missing a tremendous opportunity to onboard people who genuinely need Nostr’s freedom.
Until then, to all of the Nostr developers out there, keep up the great work and keep building. Your hard work and determination is needed.
-
 @ f6488c62:c929299d
2025-05-24 05:10:20
@ f6488c62:c929299d
2025-05-24 05:10:20คุณเคยจินตนาการถึงอนาคตที่ AI มีความฉลาดเทียบเท่ามนุษย์หรือไม่? นี่คือสิ่งที่ Sam Altman ซีอีโอของ OpenAI และทีมพันธมิตรอย่าง SoftBank, Oracle และ MGX กำลังผลักดันผ่าน โครงการ Stargate! โครงการนี้ไม่ใช่แค่เรื่องเทคโนโลยี แต่เป็นก้าวกระโดดครั้งใหญ่ของมนุษยชาติ! Stargate คืออะไร? Stargate เป็นโปรเจกต์สร้าง ศูนย์ข้อมูล AI ขนาดยักษ์ที่ใหญ่ที่สุดในประวัติศาสตร์ ด้วยเงินลงทุนเริ่มต้น 100,000 ล้านดอลลาร์ และอาจสูงถึง 500,000 ล้านดอลลาร์ ภายในปี 2029! เป้าหมายคือการพัฒนา Artificial General Intelligence (AGI) หรือ AI ที่ฉลาดเทียบเท่ามนุษย์ เพื่อให้สหรัฐฯ ครองความเป็นผู้นำด้าน AI และแข่งขันกับคู่แข่งอย่างจีน โครงการนี้เริ่มต้นที่เมือง Abilene รัฐเท็กซัส โดยจะสร้างศูนย์ข้อมูล 10 แห่ง และขยายไปยังญี่ปุ่น สหราชอาณาจักร และสหรัฐอาหรับเอมิเรตส์ ทำไม Stargate ถึงสำคัญ?
นวัตกรรมเปลี่ยนโลก: AI จาก Stargate จะช่วยพัฒนาวัคซีน mRNA รักษามะเร็งได้ใน 48 ชั่วโมง และยกระดับอุตสาหกรรมต่าง ๆ เช่น การแพทย์และความมั่นคงแห่งชาติสร้างงาน: คาดว่าจะสร้างงานกว่า 100,000 ตำแหน่ง ในสหรัฐฯ
พลังงานมหาศาล: ศูนย์ข้อมูลอาจใช้พลังงานถึง 1.2 กิกะวัตต์ เทียบเท่ากับเมืองขนาดใหญ่!
ใครอยู่เบื้องหลัง? Sam Altman ร่วมมือกับ Masayoshi Son จาก SoftBank และได้รับการสนับสนุนจาก Donald Trump ซึ่งผลักดันนโยบายให้ Stargate เป็นจริง การก่อสร้างดำเนินการโดย Oracle และพันธมิตรด้านพลังงานอย่าง Crusoe Energy Systems ความท้าทาย? ถึงจะยิ่งใหญ่ แต่ Stargate ก็เจออุปสรรค ทั้งปัญหาการระดมทุน ความกังวลเรื่องภาษีนำเข้าชิป และการแข่งขันจากคู่แข่งอย่าง DeepSeek ที่ใช้โครงสร้างพื้นฐานน้อยกว่า แถม Elon Musk ยังออกมาวิจารณ์ว่าโครงการนี้อาจ “ไม่สมจริง” แต่ Altman มั่นใจและเชิญ Musk ไปดูไซต์งานที่เท็กซัสเลยทีเดียว! อนาคตของ Stargate ศูนย์ข้อมูลแห่งแรกจะเริ่มใช้งานในปี 2026 และอาจเปลี่ยนโฉมวงการ AI ไปตลอดกาล นี่คือก้าวสำคัญสู่ยุคใหม่ของเทคโนโลยีที่อาจเปลี่ยนวิถีชีวิตของเรา! และไม่ใช่ประตูดวงดาวแบบในหนังนะ! ถึงชื่อ Stargate จะได้แรงบันดาลใจจากภาพยนตร์ sci-fi อันโด่งดัง แต่โครงการนี้ไม่ได้พาเราไปยังดวงดาวอื่น มันคือการเปิดประตูสู่โลกแห่ง AI ที่ทรงพลัง และอาจเปลี่ยนอนาคตของมนุษยชาติไปเลย! และไม่เหมือน universechain ของ star ของผมนะครับ
Stargate #AI #SamAltman #OpenAI #อนาคตของเทคโนโลยี
-
 @ c1d77557:bf04ec8b
2025-05-24 05:02:26
@ c1d77557:bf04ec8b
2025-05-24 05:02:26O 567br é uma plataforma de entretenimento online que tem se destacado pela sua inovação, variedade de jogos e foco na experiência do jogador. Com uma interface amigável e recursos de alta qualidade, a plataforma oferece uma jornada divertida e segura para os seus usuários. Neste artigo, vamos explorar os principais aspectos do 567br, incluindo a introdução da plataforma, os jogos que ela oferece e como a experiência do jogador é aprimorada em cada detalhe.
O 567br foi desenvolvido com o objetivo de proporcionar aos jogadores uma experiência imersiva e prazerosa. Sua interface é simples, intuitiva e de fácil navegação, permitindo que os usuários encontrem rapidamente seus jogos favoritos. A plataforma também é otimizada para dispositivos móveis, o que significa que os jogadores podem acessar seus jogos em qualquer lugar e a qualquer momento, seja no computador ou no smartphone.
Além disso, o 567brse preocupa com a segurança de seus usuários, implementando tecnologias de criptografia de ponta para garantir que todos os dados pessoais e financeiros estejam protegidos. A plataforma também oferece suporte ao cliente de alta qualidade, disponível 24/7, para resolver quaisquer dúvidas ou problemas que possam surgir durante a experiência de jogo.
Jogos Empolgantes e Variedade para Todos os Gostos No 567br, a diversidade de jogos é um dos pontos fortes da plataforma. Desde jogos de mesa e cartas até opções de entretenimento mais dinâmicas e inovadoras, há algo para todos os gostos e preferências. Os jogos disponíveis são desenvolvidos por alguns dos melhores fornecedores de conteúdo da indústria, garantindo gráficos de alta qualidade, jogabilidade fluida e mecânicas envolventes.
Os jogadores podem escolher entre diferentes categorias, como:
Jogos de Mesa: Para quem gosta de uma experiência mais estratégica e de tomada de decisões, os jogos de mesa são uma excelente opção. São oferecidas diversas variantes de jogos populares, como pôquer, blackjack, roleta, entre outros.
Jogos de Ação e Aventura: Para os que buscam adrenalina e emoção, a plataforma oferece uma seleção de jogos de ação e aventura com temas envolventes e gráficos impressionantes. Esses jogos garantem uma experiência de jogo emocionante e desafiadora.
Jogos de Arcade: Se você está em busca de algo mais descontraído e divertido, os jogos de arcade são uma excelente escolha. Eles são rápidos, fáceis de entender e proporcionam diversão instantânea.
A plataforma está sempre atualizando seu portfólio de jogos para garantir que os jogadores tenham acesso às últimas novidades e inovações do mundo do entretenimento online.
A Experiência do Jogador: Personalização e Interatividade O 567br não se limita a oferecer apenas uma plataforma de jogos, mas também busca criar uma experiência personalizada e interativa para cada jogador. A plataforma possui funcionalidades que permitem que os usuários ajustem sua experiência de jogo de acordo com suas preferências individuais.
A personalização da interface é um exemplo claro disso. O jogador pode escolher o tema e a disposição dos elementos na tela, criando um ambiente que seja confortável e agradável de usar. Além disso, o 567br oferece recursos interativos, como chats ao vivo, onde os jogadores podem interagir com outros usuários e até mesmo com os dealers, proporcionando uma sensação de comunidade.
Outro aspecto importante é a possibilidade de acompanhar o desempenho e os resultados de jogo. A plataforma oferece relatórios detalhados, permitindo que os jogadores monitorem seu progresso, analisem suas vitórias e perdas, e façam ajustes em sua estratégia de jogo.
Promoções e Benefícios para os Jogadores O 567br também oferece uma série de promoções e benefícios que tornam a experiência de jogo ainda mais atrativa. Novos jogadores podem aproveitar bônus de boas-vindas e outras ofertas especiais, enquanto jogadores regulares podem se beneficiar de programas de fidelidade e promoções exclusivas.
Essas ofertas ajudam a aumentar a diversão e proporcionam mais oportunidades para que os jogadores explorem novos jogos e tenham uma experiência ainda mais rica. Além disso, o sistema de recompensas é transparente e justo, garantindo que todos os jogadores tenham as mesmas oportunidades de aproveitar os benefícios.
Conclusão: Uma Plataforma Completa para Todos os Gostos Com sua interface intuitiva, variedade de jogos e foco na experiência do jogador, o 567br se consolida como uma plataforma de entretenimento online de alta qualidade. Seja para quem busca jogos estratégicos, ação intensa ou diversão casual, o 567br tem algo para todos.
A segurança, o suporte ao cliente e a personalização da experiência de jogo tornam o 567br uma opção atraente para jogadores que buscam mais do que apenas uma plataforma de jogos – buscam uma jornada de entretenimento envolvente e segura. Se você está procurando por uma experiência completa e agradável, o 567br é, sem dúvida, uma excelente escolha.
-
 @ 3bf0c63f:aefa459d
2024-09-06 12:49:46
@ 3bf0c63f:aefa459d
2024-09-06 12:49:46Nostr: a quick introduction, attempt #2
Nostr doesn't subscribe to any ideals of "free speech" as these belong to the realm of politics and assume a big powerful government that enforces a common ruleupon everybody else.
Nostr instead is much simpler, it simply says that servers are private property and establishes a generalized framework for people to connect to all these servers, creating a true free market in the process. In other words, Nostr is the public road that each market participant can use to build their own store or visit others and use their services.
(Of course a road is never truly public, in normal cases it's ran by the government, in this case it relies upon the previous existence of the internet with all its quirks and chaos plus a hand of government control, but none of that matters for this explanation).
More concretely speaking, Nostr is just a set of definitions of the formats of the data that can be passed between participants and their expected order, i.e. messages between clients (i.e. the program that runs on a user computer) and relays (i.e. the program that runs on a publicly accessible computer, a "server", generally with a domain-name associated) over a type of TCP connection (WebSocket) with cryptographic signatures. This is what is called a "protocol" in this context, and upon that simple base multiple kinds of sub-protocols can be added, like a protocol for "public-square style microblogging", "semi-closed group chat" or, I don't know, "recipe sharing and feedback".
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 3bf0c63f:aefa459d
2024-06-19 16:13:28
@ 3bf0c63f:aefa459d
2024-06-19 16:13:28Estórias
-
 @ da8b7de1:c0164aee
2025-05-23 16:08:53
@ da8b7de1:c0164aee
2025-05-23 16:08:53Amerikai Nukleáris Fordulat és Pénzügyi hatások
Donald Trump elnök bejelentette, hogy végrehajtási rendeleteket ír alá a nukleáris energia fellendítésére . Ezek célja az új reaktorok engedélyezési folyamatának egyszerűsítése, az üzemanyag-ellátási láncok megerősítése, valamint a hazai ipar támogatása az orosz és kínai nyersanyagfüggőség csökkentése érdekében. A hír hatására az amerikai és globális nukleáris részvények jelentős emelkedést mutattak: az Uránium Energy 11%, a Centrus Energy 19,6%, az Oklo 16%, a Nano Nuclear 15%, a Nu Power 14,1%, a Global X Uranium ETF pedig 9%-kal erősödött . A növekvő energiaigény, különösen a mesterséges intelligencia által hajtott adatközpontok miatt, tovább növeli a nukleáris energia stratégiai szerepét az USA-ban .
Európai és Nemzetközi Nukleáris Fejlemények
Svédország parlamentje elfogadta az új állami támogatási keretrendszert, amely akár 5 000 MW új nukleáris kapacitás beruházását ösztönzi . Az intézkedés célja az áramárak stabilizálása, az ellátásbiztonság növelése és a zöld átmenet támogatása. A program keveri az állami hiteleket és a piaci árgaranciákat (CfD), a projektek finanszírozásában pedig a magántőke is részt vesz. A törvény 2025. augusztus 1-jén lép hatályba, a végrehajtás azonban még EU-jóváhagyásra vár .
Nukleáris Ellátási Lánc és Iparági Konferencia
Május 20–21-én Varsóban rendezték meg az első World Nuclear Supply Chain Conference-t, amelynek célja a globális nukleáris ellátási lánc megerősítése és bővítése . A konferencián elhangzottak szerint az iparág előtt álló kihívás a kapacitás gyors növelése, hiszen a cél a globális nukleáris kapacitás megháromszorozása 2050-ig. A World Nuclear Association legfrissebb elemzése szerint a következő 15 évben akár 2 billió dollár értékű beruházási lehetőség nyílhat a nemzetközi ellátási láncban . A rendezvényen kiemelték az innováció, a lokalizáció és az iparági együttműködés fontosságát, valamint a szállítási és geopolitikai kihívásokat is.
Új Projektek, Technológiai és Piaci Hírek
Az Egyesült Államokban a Tennessee Valley Authority (TVA) benyújtotta az első hivatalos engedélykérelmet egy BWRX-300 típusú kis moduláris reaktor (SMR) építésére a Clinch River telephelyen . Indiában a nukleáris hatóság jóváhagyta a Mahi Banswara Rajasthan Atomerőmű négy új blokkjának helyszínét . Kínában befejeződött a Haiyang 3 atomerőmű gőzturbinájának fő egységeinek telepítése . Belgiumban és Dániában is újraértékelik a nukleáris energia szerepét, míg Brazília Oroszországgal közös SMR-projektet tervez .
Iparági Trendek és Kilátások
A World Nuclear Association és az International Energy Agency (IEA) szerint a globális nukleáris energiatermelés 2025-ben minden korábbinál magasabb szintet érhet el, köszönhetően az új reaktorok üzembe helyezésének és a stabil, alacsony kibocsátású energiaforrások iránti növekvő igénynek . A nukleáris üzemanyag-ellátási lánc megerősítése, az uránbányászat, az átalakítás és a dúsítás bővítése, valamint a szállítási kapacitás fejlesztése mind kulcsfontosságú tényezők lesznek a következő években .
Hivatkozások
reuters.com
investopedia.com
nucnet.org
world-nuclear-news.org
world-nuclear.org -
 @ 3bf0c63f:aefa459d
2024-06-13 15:40:18
@ 3bf0c63f:aefa459d
2024-06-13 15:40:18Why relay hints are important
Recently Coracle has removed support for following relay hints in Nostr event references.
Supposedly Coracle is now relying only on public key hints and
kind:10002events to determine where to fetch events from a user. That is a catastrophic idea that destroys much of Nostr's flexibility for no gain at all.- Someone makes a post inside a community (either a NIP-29 community or a NIP-87 community) and others want to refer to that post in discussions in the external Nostr world of
kind:1s -- now that cannot work because the person who created the post doesn't have the relays specific to those communities in their outbox list; - There is a discussion happening in a niche relay, for example, a relay that can only be accessed by the participants of a conference for the duration of that conference -- since that relay is not in anyone's public outbox list, it's impossible for anyone outside of the conference to ever refer to these events;
- Some big public relays, say, relay.damus.io, decide to nuke their databases or periodically delete old events, a user keeps using that big relay as their outbox because it is fast and reliable, but chooses to archive their old events in a dedicated archival relay, say, cellar.nostr.wine, while prudently not including that in their outbox list because that would make no sense -- now it is impossible for anyone to refer to old notes from this user even though they are publicly accessible in cellar.nostr.wine;
- There are topical relays that curate content relating to niche (non-microblogging) topics, say, cooking recipes, and users choose to publish their recipes to these relays only -- but now they can't refer to these relays in the external Nostr world of
kind:1s because these topical relays are not in their outbox lists. - Suppose a user wants to maintain two different identities under the same keypair, say, one identity only talks about soccer in English, while the other only talks about art history in French, and the user very prudently keeps two different
kind:10002events in two different sets of "indexer" relays (or does it in some better way of announcing different relay sets) -- now one of this user's audiences cannot ever see notes created by him with their other persona, one half of the content of this user will be inacessible to the other half and vice-versa. - If for any reason a relay does not want to accept events of a certain kind a user may publish to other relays, and it would all work fine if the user referenced that externally-published event from a normal event, but now that externally-published event is not reachable because the external relay is not in the user's outbox list.
- If someone, say, Alex Jones, is hard-banned everywhere and cannot event broadcast
kind:10002events to any of the commonly used index relays, that person will now appear as banned in most clients: in an ideal world in which clients followednprofileand other relay hints Alex Jones could still live a normal Nostr life: he would print business cards with hisnprofileinstead of annpuband clients would immediately know from what relay to fetch his posts. When other users shared his posts or replied to it, they would include a relay hint to his personal relay and others would be able to see and then start following him on that relay directly -- now Alex Jones's events cannot be read by anyone that doesn't already know his relay.
- Someone makes a post inside a community (either a NIP-29 community or a NIP-87 community) and others want to refer to that post in discussions in the external Nostr world of
-
 @ d360efec:14907b5f
2025-05-13 00:39:56
@ d360efec:14907b5f
2025-05-13 00:39:56🚀📉 #BTC วิเคราะห์ H2! พุ่งชน 105K แล้วเจอแรงขาย... จับตา FVG 100.5K เป็นจุดวัดใจ! 👀📊
จากากรวิเคราะห์ทางเทคนิคสำหรับ #Bitcoin ในกรอบเวลา H2:
สัปดาห์ที่แล้ว #BTC ได้เบรคและพุ่งขึ้นอย่างแข็งแกร่งค่ะ 📈⚡ แต่เมื่อวันจันทร์ที่ผ่านมา ราคาได้ขึ้นไปชนแนวต้านบริเวณ 105,000 ดอลลาร์ แล้วเจอแรงขายย่อตัวลงมาตลอดทั้งวันค่ะ 🧱📉
ตอนนี้ ระดับที่น่าจับตาอย่างยิ่งคือโซน H4 FVG (Fair Value Gap ในกราฟ 4 ชั่วโมง) ที่ 100,500 ดอลลาร์ ค่ะ 🎯 (FVG คือโซนที่ราคาวิ่งผ่านไปเร็วๆ และมักเป็นบริเวณที่ราคามีโอกาสกลับมาทดสอบ/เติมเต็ม)
👇 โซน FVG ที่ 100.5K นี้ ยังคงเป็น Area of Interest ที่น่าสนใจสำหรับมองหาจังหวะ Long เพื่อลุ้นการขึ้นในคลื่นลูกถัดไปค่ะ!
🤔💡 อย่างไรก็ตาม การตัดสินใจเข้า Long หรือเทรดที่บริเวณนี้ ขึ้นอยู่กับว่าราคา แสดงปฏิกิริยาอย่างไรเมื่อมาถึงโซน 100.5K นี้ เพื่อยืนยันสัญญาณสำหรับการเคลื่อนไหวที่จะขึ้นสูงกว่าเดิมค่ะ!
เฝ้าดู Price Action ที่ระดับนี้อย่างใกล้ชิดนะคะ! 📍
BTC #Bitcoin #Crypto #คริปโต #TechnicalAnalysis #Trading #FVG #FairValueGap #PriceAction #MarketAnalysis #ลงทุนคริปโต #วิเคราะห์กราฟ #TradeSetup #ข่าวคริปโต #ตลาดคริปโต


-
 @ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03
@ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ c1d77557:bf04ec8b
2025-05-24 05:01:44
@ c1d77557:bf04ec8b
2025-05-24 05:01:44O P11Bet é uma plataforma inovadora que chega para oferecer uma experiência de jogo única, reunindo uma variedade de opções para os entusiastas de diferentes tipos de entretenimento online. Com uma interface moderna e fácil de usar, ela se destaca por proporcionar uma jornada divertida e segura para os jogadores, com um foco especial na qualidade da experiência e no atendimento às necessidades do público.
Uma Plataforma Completa e Acessível Ao acessar o P11Bet, os usuários encontram uma plataforma intuitiva, que facilita a navegação e oferece uma variedade de recursos para tornar o jogo mais agradável. A estrutura do site é otimizada para fornecer uma experiência fluida, seja no desktop ou em dispositivos móveis. Além disso, a plataforma se preocupa em manter um ambiente seguro, garantindo a proteção dos dados dos jogadores e permitindo que se concentrem na diversão.
A plataforma é projetada para todos os tipos de jogadores, desde os iniciantes até os mais experientes. A simplicidade de uso é uma das grandes vantagens, permitindo que qualquer pessoa possa se registrar e começar a jogar sem dificuldades. Além disso, a p11betoferece suporte ao cliente em português, o que facilita a comunicação e garante um atendimento de alta qualidade para os usuários brasileiros.
Diversidade de Jogos para Todos os Gostos O P11Bet se destaca pela vasta gama de opções de jogos que oferece aos seus usuários. A plataforma abriga uma seleção diversificada que vai desde jogos clássicos até as opções mais modernas, atendendo a todos os estilos e preferências. Entre as opções mais procuradas estão jogos de mesa, apostas esportivas, slots, e outras modalidades que garantem horas de entretenimento.
Um dos principais atrativos do P11Bet são os jogos de habilidade e de sorte, que exigem tanto estratégia quanto um pouco de sorte. As opções variam desde os mais simples aos mais complexos, oferecendo algo para todos os gostos. Os jogadores podem se aventurar em diversas modalidades, testando suas habilidades em jogos que vão de roletas e blackjack a versões mais inovadoras e dinâmicas.
Para aqueles que preferem algo mais emocionante e competitivo, as apostas esportivas são uma das maiores atrações. O P11Bet oferece uma ampla variedade de eventos esportivos ao vivo para apostar, com odds atrativas e uma plataforma que permite realizar apostas de forma rápida e eficiente. Seja em esportes populares como futebol, basquete ou até mesmo esportes menos tradicionais, há sempre algo para os apostadores mais exigentes.
A Experiência do Jogador: Diversão e Segurança O P11Bet não apenas se preocupa com a diversidade de jogos, mas também com a experiência do jogador. A plataforma foi desenvolvida para garantir que os jogadores possam desfrutar de seus jogos favoritos com a maior segurança e conforto possível. Além de um design intuitivo, a plataforma oferece diversas opções de pagamento, incluindo métodos populares no Brasil, para facilitar depósitos e retiradas. Isso garante que o processo de transações seja simples, rápido e seguro.
Outro ponto positivo do P11Bet é a experiência imersiva que ele oferece aos jogadores. A plataforma está sempre atualizada com novas funcionalidades, com promoções atraentes e bônus especiais que aumentam ainda mais a diversão. A interação com outros jogadores também é um diferencial, com espaços que permitem competir, conversar e trocar experiências com pessoas de todo o mundo.
Além disso, o suporte ao cliente da P11Bet é um dos mais elogiados pelos usuários. A equipe está sempre disponível para resolver dúvidas e fornecer assistência de maneira eficaz e amigável. Isso garante que os jogadores tenham sempre uma experiência tranquila, sem se preocupar com questões técnicas ou problemas relacionados à plataforma.
Conclusão Em resumo, o P11Bet é uma excelente escolha para quem busca uma plataforma completa e de qualidade para se divertir e desafiar suas habilidades. Com uma grande variedade de jogos, uma interface de fácil navegação e um suporte excepcional, ele garante que cada momento na plataforma seja único e prazeroso. Para quem deseja se aventurar no mundo dos jogos online, o P11Bet é uma opção que combina segurança, inovação e diversão.
-
 @ bc6ccd13:f53098e4
2025-05-24 15:55:20
@ bc6ccd13:f53098e4
2025-05-24 15:55:20It wasn’t so long ago that the mainstream conversation around population was exclusively focused on the dangers of overpopulation. The fatal flaws in the Malthusian theory had yet to be disproven clearly and obviously by observable demographic trends. That’s been gradually changing, and while it’s hardly a mainstream consensus, concerns about falling birthrates and the risk of population collapse have taken over the population conversion on the political right, and sometimes beyond.
There’s no questioning the data at this point. Fertility rates over most of the world have been in precipitous decline, and if the current trajectory continues, global population will peak very soon and fall rather dramatically. And even the falling population itself is much less of a threat than the aging population that will inevitably precede it. Having a large cohort of older and retired people and a small cohort of young workers is an existential threat to the modern welfare state, and to the entire credit-based fiat monetary system that supports it. But that’s a subject for another day.
There are a multitude of different theories that attempt to explain why this is happening. I’ll name some of the most common ones:
-
Increased education and employment opportunities for women
-
Urbanization
-
Economic factors
-
Access to contraception
-
Changing social and cultural norms
-
Delayed marriage
-
Improvements in infant mortality rates
-
Government policies
-
Environmental concerns
-
Pornography
-
Feminism
-
Endocrine disrupting chemicals
-
Dating apps
Most rational thinkers agree there must be multiple factors playing a role. But the fact that the problem is so wide-spread, and populations that seem to be resisting the trend are so rare, shows that the strongest underlying factors are cross-culturally powerful and not easily resisted or reversed with marginal cultural differences and standard public policy efforts.
While populations that resist the trend are rare, they are not quite non-existent. A few groups stand out for their persistently high fertility rates. On a geographic basis, sub-Saharan Africa is the only major region still maintaining above-replacement fertility rates. For various reasons, I don’t think Africa is the most useful place to look for answers on what’s causing the decline elsewhere or how it could be reversed. One reason is that Africa seems to be following the global pattern, just with a lag. In another few decades the data may look very different, just like it does for South America today compared to 20 years ago.
In my opinion, a more useful place to look for data is in smaller population sub-groups within a geographic area that have fertility rates significantly higher than the general population levels. Rural populations in general have higher fertility rates than urban populations, but the difference isn’t really enough to consider it significant. The groups that fit this category well seem to be exclusively religious. These include certain Christian denominations in the traditional Anabaptist category including the Amish, Mennonites, and Hutterites, Muslims in some areas, and Jews, particularly the most orthodox sects. Mormons recently fell out of the high-fertility religious group category, which would also make for some interesting research.
It would be fascinating to compare these groups and see what they have in common outside just being religious in nature. I don’t have the knowledge to make that comparison. Instead, I’m going to focus on the group that’s often referenced and analyzed by people without much personal knowledge, the Amish.
I have read numerous articles and comments that reference the Amish to support this or that theory on the cause of falling fertility. One thing I notice is an obvious lack of understanding of the Amish culture, which leads to faulty arguments that don’t reflect reality. This isn’t surprising, given the insular and poorly-understood nature of the culture, the plethora of ridiculously incorrect “Amish” reality TV shows and pop culture myths, and the fact that the number of people with firsthand knowledge of Amish culture from an insider perspective who also write about demographic trends on any public platform is probably zero.
Well, was zero. I’m about to make that one.
My Qualifications
Since I’m claiming to have this knowledge, it’s only fair to give a little background as to how I got it. I choose to stay anonymous on the internet, and given that this is personal information that could make it significantly easier to dox me, I’ll be deliberately vague.
My parents were both born in Amish families. They didn’t stay, opting to leave the Amish church and culture before getting married and starting their family. My grandparents were all Amish, and all my cousins and most of my extended family remain Amish to this day. My parents didn’t move out of the Amish community, staying in the area and joining a conservative Mennonite church that was about the closest thing to being Amish without actually being Amish. The Mennonite community has a generally good relationship with and a lot of respect for the Amish community, given their deep similarities and shared history and cultural background.
I grew up interacting regularly with Amish relatives, neighbors and community members, speaking the Pennsylvania Dutch my parents taught us and used exclusively at home. I’m very certain that a real deep understanding of Amish culture is almost impossible without speaking their language, just like many other cultures around the world. The Amish speak English as their second language, but there are aspects of their culture that aren’t spoken about in English.
This lifelong proximity to and interaction with the Amish community has, I believe, given me some unique insights into the factors supporting their high fertility rates that no amount of academic research will ever uncover.
Who are the Amish?
First, some basics.
The Amish are a traditionalist Christian denomination. The way to understand the Amish is as a religious denomination first, and a culture second. Getting the two mixed up makes it impossible to understand why the Amish live the way they do.
Sure, their unique lifestyles makes them noteworthy as a group. But that lifestyle is based on and maintained by their religious beliefs and convictions.
Fundamentally, the Amish attempt to live out the Gospel as Jesus taught in the Sermon on the Mount. They believe their church has done so historically, and that the best way to make sure they keep doing so in the future is to view any changes to their traditional lifestyle with extreme skepticism and resistance.
The two primary doctrines that separate them from the mainstream Protestant Reformation, which is their group’s origin, are the doctrines of nonconformity and nonresistance. They apply the doctrine of nonconformity, the command to “be not conformed to this world: but be ye transformed by the renewing of your mind, that ye may prove what is that good, and acceptable, and perfect, will of God” in both a spiritual and a practical sense. They believe that Christians are to be radically different from non-Christians, both in their beliefs and attitudes, and in their lifestyle and appearance. And they apply the command to “resist not evil”, nonresistance, to mean that it’s a sin to use physical force or violence against another person for any reason whatsoever. They don’t make any exception for military service of any type, which they object to as a matter of conscience, or for self-defense, which they refuse to engage in even if it means death for themselves or their family.
The Amish do not practice infant baptism. Their young people must choose to be baptized and formally become members of the church, usually in their late teens or early twenties. As part of the baptism ceremony, they make a vow to remain faithful to God and the church until death. The Amish, as a church, interpret this vow to mean that the new church member will remain a member of the Amish church for life. Leaving the Amish church after making this vow and being baptized is viewed as breaking the vow, and is the justification for their practice of shunning, or the ban. Those who do so are cut off from contact with the community in various ways. Typically they won’t eat a meal with a shunned person, ride in a car a shunned person is driving, or do business with a shunned person. That includes immediate family. Failure to enforce this shunning against someone, even your own child, can result in running afoul of the church leadership and also being excommunicated and shunned.
This punishment, however, only applies to people who leave the church after baptism. Those young people who choose not to be baptized and leave the church instead are free to be treated just like any other non-Amish person, although their family essentially disown them and treat them like a shunned person anyway, if they’re especially strict and upset about the betrayal of Amish values.
Most Amish people don’t believe that the Amish are the only true church, or that only Amish people are true Christians. Most are accepting of other conservative Anabaptist denominations, and respect their values and practices as a different but valid way to be Christian. Church teaching strongly suggests that those who fall under the ban are living in sin and won’t make it to heaven. Most individuals, though, probably wouldn’t agree with that in every case if they were free to give their true opinion on the issue.
The Amish maintain a fertility rate of around 6 to 7 children per woman. Some recent research suggests this may be starting to fall somewhat, but the data isn’t extensive enough to make a solid judgement yet.
There are a wide variety of different “flavors” of Amish in different areas of the US, a fact they’re very aware of. The data strongly indicates that the most conservative and technologically primitive communities have slightly higher fertility rates and significantly higher retention rates of young people.
Why do the Amish Maintain High Fertility Rates?
Okay, enough background. Time to dive into the reasons I believe the Amish maintain their historically high fertility rate despite living in a developed, modern economy surrounded by people with dramatically sub-replacement fertility rates.
I thought long and hard about the best way to approach this. Going through a list of factors topically seemed like the obvious one. But the more I thought it through, the less I liked it. For one, how do you arrange the factors? Order of importance? How do you decide that? Also, the factors are so inter-related that they’ll be very tough to separate and understand individually. Finally, it seems dry and boring. Nobody needs that.
So I’m going to try something different. I’m going to approach it from a narrative angle. I’ll try to describe the life of a typical Amish person, from birth to death, in a chronological way. That’s the best approach to present it in a way that makes the culture relatable, while also tying the different factors together logically.
I’ll describe the experience for both men and women as best I can, and try to present the various factors encouraging high fertility as I see them at the appropriate part of the story.
This will likely be an article that gets revised later to address any questions that come up, so don’t consider it the final word on the subject.
Alright, time to get started.
Subscribed
First off, this might seem obvious, but the typical Amish baby is born into a large family. On average, they’ll have 5 or 6 siblings, and more is not at all uncommon. Families of 10 won’t raise an eyebrow, and 12-16 children aren’t unheard of, especially in the past when mortality was higher and second marriages were more common among younger widowers who went on to have children with their second wife. Humans are social creatures, and the environment and people we grow up surrounded by have a strong influence on our frame of reference. Studies have shown that women are very unlikely to have more children than their mother had. The number of siblings in your family, and in families you observe and interact with, doesn’t determine the number of children you will have, but it does strongly influence the number of children you feel is a “normal” amount. That makes it a kind of ratchet effect, where it’s very unlikely that a generation raised in homes with one or two children will go on to have larger families of their own collectively.
This cultural norm of large families establishes a kind of inertia that normalizes high fertility right from birth. Amish children grow up surrounded by siblings, observing, and as they get older, helping with the care and maintenance of a large family. All their relatives, cousins and extended family are also likely to belong to large families. The average Amish child grows up with dozens of first cousins, and sometimes hundreds of more distant cousins, many of whom they likely know well and socialize with regularly. This experience establishes a mental framework where a large family is assumed to be the default. And there is no stronger human tendency than the urge to fit in with the people around you.
Amish children grow up with strong gender norms taught from a very young age. The Amish culture follows strict and conservative gender roles. Boys and men do male things, girls and women do female things, and there is little effort or desire to create any overlapping space.
Boys grow up doing traditionally masculine things. They play outside, do chores on the farm, help their dad with his work, probably get a BB gun before age 10, go hunting and fishing, play sports, and generally prepare for a lifetime of physical labor and providing for a wife and family.
Girls grow up doing traditionally feminine things. They help care for younger siblings, help with housework, play with dolls, learn to cook and preserve food, learn to sew, and generally prepare for a lifetime of caring for and raising children and maintaining a large household.
It’s a common misconception that the Amish are mostly farmers who live off the land, subsistence style. That’s not at all accurate. While there are still Amish who make their living farming, at least in some areas, that has become the exception. The large scale of modern agriculture means it takes a lot of acres and a lot of machinery to run a profitable commercial farming operation. The Amish reject the use of most modern agricultural machinery, which makes them uncompetitive in commercial agriculture outside more niche markets like dairy, produce, or greenhouses. And the fact that they live in small geographic communities with large families means they quickly buy up all available farmland in an area until they price themselves out of the market. Prime farmland in heavy Amish farming communities like Lancaster, Pennsylvania routinely sells for over $25,000 per acre, which is more than a commercial crop farming operation might bring in over a lifetime.
So the Amish have moved away from a primarily agriculture based economy to various other occupations. In some areas they work in RV factories. Most work in trades, primarily construction. Many are masons, carpenters, cabinet builders, mechanics, welders, etc.
But they reject the ownership of cars, so they still use their characteristic horses and buggies for transportation. In reality, they use cars for most of their transportation needs. But they don’t own cars or have driver’s licenses, so they rely on “Amish taxi drivers” to chauffer them around. The men hire a driver to take them to and from work, if they work in construction or some other job outside the home. The women hire a driver take them to town for their shopping or for other errands. The exception is church. They’re still required to drive to church in a horse and buggy, so every family must keep a horse for that reason, as a bare minimum. In many cases that’s the only time they ever use a horse and buggy, and if it weren’t for that requirement they wouldn’t own one at all.
But that requirement means every Amish family must own enough land to keep a horse, which takes a few acres and a small barn at minimum. This forces them to live in rural areas and raise their families in a somewhat agricultural environment, even if their occupation wouldn’t require that at all. So there are always chores for the children, animals to care for, and space to play outside with their siblings.
Amish children grow up with very limited exposure to mainstream cultural pressures. Their mothers inevitably raise them at home until they start school. They don’t have TV or cell phones, so they aren’t exposed to any mainstream culture on a daily basis.
The Amish have their own schools, typically small one room schools within walking distance of all the families who attend. The teachers are often young single people, always Amish. They primarily teach basic academics: reading, writing, arithmetic, geography, history, etc. While the Amish speak both English and Pennsylvania Dutch, many Amish children are first exposed to English on a daily basis when they start school. School is taught in English, although there is limited teaching of the High German the Amish use in their church services.
Amish children attend school until 8th grade. The schools run the minimum number of days required by the state, usually 160. There is no higher education beyond grade 8. No Amish attend college.
Amish children are taught from little up that they are not like other people. The differences between their culture and mainstream culture are emphasized, and Amish culture is praised as the ideal, at a religious level. They're taught that the way to do what’s right is to do what the church asks, and those who don’t do what the church asks are in the wrong.
The Amish rate and describe everyone on a scale from “high” to “low”. A person who isn’t Amish, who isn’t a Christian, is a “high” person, or an “English” person. To go from being Amish to being “English” is the worst, most damning, failure imaginable. The Amish are “low” people. The more strict and traditional an Amish sect, the “lower” they are. Being “low” is seen as a virtue. Other conservative Christian denominations, particularly other Anabaptist groups, are also considered “low” people and generally viewed favorably, but they aren’t as “low” as the Amish.
Amish boys grow up expecting to start work full time at age 14, and to work at some type of trade or physical labor. There are no white-collar career tracks, essentially. Entrepreneurship is encouraged, and many young Amish men start their own construction crew or home business in their 20s or 30s after a few years of experience working for someone else. Often Amish boys start off working for and with their dad, in whatever trade or business he operates. But if they’re not interested in that particular occupation, they’re free to find another. Amish businesses and tradesmen are always willing to hire young Amish boys and train them in a craft. A good work ethic is considered a virtue, and Amish are known for their skilled craftsmanship and willingness to work harder than the competition. These traits are taught and encouraged from little on up.
Amish men as a whole do very well financially. For one, they start working and developing skills and work ethic a decade earlier than the typical college graduate. The trades pay well, and of course anyone could take advantage of that, but the mainstream narrative discourages men from pursuing a trade career by labeling it low status and keeping them in education until their prime years to gain a work ethic are past. It’s not uncommon for young Amish men just out of 8th grade to land a job on a carpentry crew for $25-30 an hour. With bonuses, some of them are bringing in $90k/year before age 20. Another advantage young Amish men have is lower expenses. They can certainly find places to spend their money, typically hobbies like hunting and fishing, but things like expensive designer clothes and accessories or overpriced car payments aren’t really an option. They also benefit from the Amish exemption to Social Security taxes. The Amish don’t pay into or collect Social Security. More on that later, but it helps immensely to keep more of your paycheck in your early prime working years.
Amish girls grow up expecting to get married at a young age and raise a large family as a traditional housewife. Amish girls aren’t encouraged to have a “career”, and the idea would be silly to them. They are expected to work, but the work is either helping their mom with the household, working on the family farm or business, or doing something like teaching school or working at an Amish farmer’s market to pass the time between leaving school and marriage. It’s never viewed as a permanent occupation, because marriage and motherhood is the default aspirational lifestyle. A common job for young Amish girls is working as a “maid” to help a new mother with housework at the end of pregnancy and for the first few months after childbirth. All new mothers can get this type of help if they want, and it will usually be a younger sister, cousin, or niece of appropriate age. Otherwise the community will find a suitable girl who’s available for the job. A “maid” will sometimes travel to a different Amish community for this reason, given how large extended families are and how frequently Amish families move across the country to a different community. This is often an opportunity for them to attract the attention of a young man outside their local community, and is one of the only ways for a long-distance relationship and marriage to begin.
Amish young people are expected to live with their parents until marriage, with very few exceptions. They’re also typically expected to work for their dad in the family business for no pay, and to give any earnings they make at a day job outside the home to their parents. This is typically expected until age 21, or until they get married, whichever comes first. More recently, with the rising cost of land and housing, it’s becoming more common to make age 18 the cutoff. And when a young couple is engaged, the parents typically allow them to start saving their income for their future household. This practice helps parents offset some of the expenses of raising such large families, along with the fact that no money is spent on higher education. It also provides one strong incentive to marry as early as possible.
Amish culture revolves around family and the community. Extended families are large, and people are expected to know and interact with their family. Conversation with a stranger at a social event invariably starts by asking their name, then asking who their parents, grandparents, and other relatives are until some distant family connection or a mutual acquaintance is found. Since the Amish community has a small pool of family names, and tends to heavily favor certain Biblical first names, enough people end up with the same name to make things really confusing. People are often identified by two or three generations of their family, for example “Sam Yoder’s John’s Amos” for an Amos Yoder who’s father was John Yoder and grandfather Sam Yoder.
Social activities are either family events or church events, or both. Weddings and funerals are the main social functions other than church services, and people are expected to attend as many as possible among their family and extended family, regardless of the distance. Given the large family sizes, most Amish have dozens of first cousins and many more distant cousins. Weddings and funerals can be almost weekly events. These are church events as well, so much of the local Amish community will usually attend. It will be an all day event, with the women and girls preparing a lunch and dinner for everyone. After the meal, the women and girls will wash the dishes and clean up, while the men sit around and talk. No cell phones, remember. Talking is the main form of social interaction. Topics typically include work, family news, hunting and fishing stories (Amish men hunt and fish with the same enthusiasm typical American men watch sports), horses, and interesting or funny stories about family and friends. Those with a knack for entertaining oratory are well respected and appreciated in the Amish community.
Of course the women do their fair share of talking as well, in the kitchen while cleaning up after the meal, and later in the living room where they join the men after the domestic work is done. The main topics of conversation always revolve around family, immediate and extended. News travels through the Amish community faster than any social media platform, because nothing builds Amish female status more than being the first to call with the news that great uncle so-and-so was injured in a farming accident or nephew so-and-so has a new baby, along with all the pertinent details about the name, size, and health of the baby and how the mother is doing and how many grandchildren that makes in total for the lucky grandparents.
While the adults are talking, the children are free to play either inside or preferably outside. Trampolines, climbing trees, playing in the hayloft, tag, volleyball, and softball are favorite activities at various ages. The younger boys and girls typically play together, but as they get older the girls spend more time visiting while the boys prefer more structured sports. Softball is a game for boys, but volleyball is popular with mixed teams of boys and girls at any age.
Visiting relatives or other community families is also a popular social activity, especially on “in-between Sunday”. The Amish have church every other week, and the week without church is often an opportunity to visit another family. Invitations are not expected or required, and anyone stopping by will be expected to stay for dinner and into the evening. At these type of events, the older children are often expected to sit and visit with the adults. Sitting still and being quiet are mandatory skills, since church services are 2 hours or longer and held in barns or sheds without air conditioning filled with backless wooden benches. Self-discipline is not an optional virtue, because the alternative is physical discipline.
As Amish young people enter their mid teen years, they go from childhood to youth. At a certain age, usually around 15 or 16, they officially become youth and enter the stage everyone is familiar with, “rumspringa”. That’s a Pennsylvania Dutch word that translates to “running around”. The Amish use it more as a verb, but pop culture has adopted it as a noun based on some wildly inaccurate reality TV shows and depictions.
The reality is, rumspringa varies widely from community to community, mostly based on what the parents and church leaders tolerate. Remember that Amish church membership is a fully voluntary decision, and Amish young people are free to join or not, as they decide. Late teens is the typical age for that decision. In the meantime, they are free to make their own decisions, subject to their parents’ rules. Breaking the rules can mean that at some point, they won’t be welcome to live in their parents’ household any more. That’s a fairly strong deterrent to the most extreme infractions.
At this stage, young Amish men will be buying their own horse and buggy, and both boys and girls will be permitted to attend the Sunday night “singing”. This is a social activity held at someone's house on Sunday evening, involving all the youth in the community coming together for dinner, playing volleyball, and singing German hymns together. The purpose is to provide a somewhat controlled social environment for young men and women to interact and hopefully meet their future spouse. Dating couples can attend together, and dates are permitted after the formal activities, with the young men often driving their date home late at night before finally heading home themselves.
Depending on the tolerance of the community, the informal activities can be a bit more permissive than singing hymns and playing volleyball. Often the buggies will become a typical teenage party scene, with alcohol, smoking, a radio, illicit smartphones and DVD players, and some less-than-reserved interaction between boys and girls. The punishment for getting caught can be severe, but in many cases the adults tend to turn a blind eye to what’s happening, and let the young people do as they please.
A lot more could be said about the dynamics of this cultural practice, but specifics vary so much between communities that I don’t think there’s much value in doing so. The point I think is relevant to this discussion is the question of sex.
There’s no reason to go off into the weeds on how much, if any, sex occurs. Premarital sex is absolutely forbidden. Does it happen anyway? Humans being human, certainly. How much? Probably very little in most cases. Getting pregnant, or getting someone pregnant, is the one transgression with inevitable life-changing consequences. The “shotgun wedding” is alive and well among the Amish, and getting a girl pregnant means marrying her or being expelled from the Amish community permanently, no exceptions. Besides that, getting pregnant outside of marriage is the most disgraceful and shameful thing a girl could do. It happens very very rarely, put it that way.
So casual sex within the community is basically off the table. What about casual sex with “English” people? This is where the Amish cultural practices play a big role. The Amish dress very distinctly. They can’t go anywhere in their traditional clothes without being instantly recognized. They also don’t drive cars, so going somewhere means getting a ride with someone. And their parents will usually keep an eye on their plans and whereabouts. So let’s imagine how an Amish teenager might go about finding a casual sexual encounter.
First off, getting ahold of a cell phone would be essential. They need some way to communicate with the outside world, and coordinate with their “partner in crime.” A lot of Amish teenagers do this, often with the help of slightly older people who have left the Amish, but keep ties with the community, maybe an older sibling or cousin. These are often the same people who buy alcohol for Amish teens.
Then, they need to get some non-Amish clothes. Remember, every trip away from home will take a willing driver, a plausible excuse in a community where everyone knows everyone, and the guarantee of being immediately recognized if seen in public. And the Amish parents know who the “bad kids” are, the ones who left but are willing to help their younger relatives and friends break the rules. Getting caught hanging around with them will probably mean a lot less trust and a lot less freedom in the future.
For the girls, a change of “English” clothes and a new hairstyle will let them blend in quite well. Of course, they can’t be caught leaving or coming home in those clothes, or have the clothes found at home. Lots of logistical hurdles everywhere. For the boys, they have a very distinctive haircut. A new change of clothes won’t fix that. There’s really no way for them to hide the fact that they’re Amish, even if the accent and the lack of a driver’s license don’t give them away.
Assuming they manage all that, and sneak away from home undetected, how will they find someone to hook up with? They’re very insulated from popular culture, and probably not at all comfortable in typical social situations. For the girls, there’s the added risk that an accidental pregnancy, or even just getting caught, would ruin their reputation and any chance of marriage and a family in the Amish community. So they’re unlikely to even try, unless they’re already fully intending to leave the Amish for good. That only really happens if they have a guy ready to marry them outside the Amish community, for reasons I’ll get into more later. Briefly, the Amish culture and schooling leaves women poorly prepared to support themselves outside that culture.
For the boys, there’s the typical difficulty men face in finding casual sexual partners. Multiply that by the difficulty of not having a car or driver’s license, not being experienced in mainstream social norms, plus that obvious and undisguisable Amish haircut. And all that ignores the lifelong teaching that casual sex is sinful and wrong, and those who engage in it are going against the teachings of God and the church. The entire culture is specifically designed to discourage casual sex as strongly as possible, and it does an excellent job at that.
Why does that matter? Well, humans are all very much the same, with the same desires and instincts. And sex is one of the strongest of those desires. The Amish are certainly no different.
So the Amish religious practice and culture offers a very simple choice. You can choose sex outside of marriage, which will be difficult or impossible, occasional at best, and if you get caught will mean expulsion from the community your life is rooted in, and even if you don’t get caught will mean you’re committing a mortal sin that will keep you out of heaven if you don’t repent and change. Or, you can get married and have all the sex you want, and be respected and rewarded for it.
That’s really all it takes to sell the idea of marriage to most men.
When a couple does decide to get engaged, of course with permission from the girl’s father, the wedding happens within a reasonably short time, in acknowledgement of the temptation young people face in that situation.
So let’s take a little closer look at the gender differences between the choice to stay single or to marry. It’s helpful to lay out the different life paths available, and how they play out over time.
There are very few Amish who remain single throughout their life, and almost all of them are women. So let’s look at it through a man’s perspective first. What kind of life can a single Amish man expect?
First off, a lifetime of celibacy. There’s hardly any need to go further, that’s a deal breaker for most men. If they choose to stay single for some reason, most will leave the Amish completely rather than accept those terms.
So maybe it’s more useful to look at incentives for early marriage, which is the norm. I’m a strong believer that incentives create outcomes, so I’ll be taking a hard look at incentives throughout this article.
Young people are expected to live with their parents until marriage, in most cases. Remember, no going off to college either. So from age 14 on, they’re stuck living with Mom and Dad, working full time, and not even keeping their own income. That gets old fast. Getting married, moving out, and starting a family looks better every day. Besides that, Amish women do a lot to improve the lives of their men. The Amish are well known for their delicious food. Well, that’s because the Amish women cook and bake. As a single guy, moving out of Mom’s house means not getting delicious home-cooked food every day. And they don’t have an iPhone to order DoorDash either, so it’s pizza delivery, hiring a driver to go to a restaurant, or whatever you can cook yourself. And Amish boys don’t grow up learning how to cook, that’s women’s work. Same with making clothes. Amish mothers and wives sew clothes for their families, since they’re forbidden to wear commercially available clothes in general. So a single guy is dependent on his mom for new clothes as well. Same with washing clothes. Most Amish have fairly modern clothes washing machines, although they don’t use dryers. But washing and folding clothes isn’t a job most boys grow up doing, so they’re pretty lost if they have to try it.
All in all, there aren’t a lot of upsides to staying single longer than absolutely necessary. There are plenty of benefits to marriage, though. For one, marriage is seen as a necessary step to full maturity as a man. It’s even expressed as a visible marker. Single young men typically stay clean-shaven. Once they get married, shaving is completely forbidden, and they are required to grow out a full beard. So the difference between married and single men is obvious at first glance, and is acknowledged as a marker of full maturity.
Then of course there’s the sexual access. No explanation needed.
Then there are all the benefits of an improved lifestyle a stay-at-home wife provides. That includes cooking, cleaning, washing clothes, caring for a garden, preserving food, helping with farm work or chores, and helping with his business. Many Amish wives are very involved in their husband’s career or business, whether that’s managing the bookkeeping, working in the greenhouses, or helping with daily chores on the farm. While most Amish communities use quite modern household appliances, powered with batteries, kerosene, or air pressure, the work of maintaining a household is still much more involved than for the typical American household. Especially when it comes to sewing, which very few American women do at all, but which took a large percentage of women’s time only a few generations ago. Among the Amish it still does.
I’m only focusing on the incentives for marriage right now, because that’s the first step. Of course, most married couples today don’t have 5-8 children, so there’s more to the story. But universal marriage, particularly early marriage, is an essential part of the puzzle.
Shifting focus to the women, here the picture is even more clear. Almost all lifelong single Amish people are women, and that’s not by choice. The Amish still maintain the “old maid” category that used to be part of mainstream culture. Single Amish women are almost invariably single because no man offered to marry them. Here’s why.
If single life is unappealing for Amish men, it’s positively bleak for women. Marriage and family life is the aspirational goal they’re taught from little up. And for good reason.
With their eighth-grade education, and without a driver’s license and car, their income earning potential is very limited. Most young women who aren’t busy on the farm or with the family business work as schoolteachers, housecleaners, babysitters, or cooks and servers at Amish restaurants or farmers’ markets. None of these jobs pay well. Enough to buy a few personal items, but not enough to buy a house or support even one person. And while it might be acceptable for a single Amish man to eventually buy a house and move out, at some point in his late 20s or early 30s, it’s really not acceptable at any age for an Amish old maid. Those old maids typically end up living with their parents, caring for them in old age, working the same type of jobs young girls do, and probably hoping that at some point an older widower with a family will show up and propose.
Marriage has massive lifestyle benefits for women, even more so than for men. Amish men typically do well financially, and often work in construction as well, or have friends and relatives who do. Amish houses are very nice and well constructed to say the least, and the wife gets the house she wants, the way she wants it. Being stingy with a house for your wife isn’t part of an Amish man’s mentality. Amish women are well rewarded for all their hard work keeping house, with a house they’ll be happy keeping. And of course a nice farm or at least some acreage, with space for a big garden, a barn for any animals, and space for greenhouses or whatever she needs for any home business ambitions she might have.
Along with that, Amish women have a lot of flexibility when it comes to spending money. Many Amish women handle most of the family finances. And the money her husband earns is family money, not his money. While the husband has final say in financial decisions, most Amish men don’t say no to their wives’ purchase requests often. Married Amish women have access to all the creature comforts the church allows to make their lives as pleasant as possible.
When it comes to status, the benefits are just as clear. Amish life revolves around family, and nothing is higher status than a thriving family of your own. The Amish version of posting exotic vacation pictures on Instagram is showing up to a social function with your new baby. It’s the automatic center of attention for weeks, until a newer baby show up in the community. And the default topic of conversation is always a woman’s children and their growth and development. Young girls grow up dreaming of the day they can join those conversations, and old maids are always outsiders in a certain sense, pitied by everyone else for their misfortune.
Being an old maid means being poor, low status, pitied by other women, and destined to live with your parents until they pass, with your only bitter-sweet consolation being the role of aunt to your dozens of nieces and nephews and maid to your sisters and sisters-in-law through their many pregnancies. Getting married means access to a man’s income, a nice new house just the way you want it, a farm, and an automatic status boost as a mother and eventually grandmother who always has lots to contribute to the conversation at social events.
As you can imagine, the incentives strongly favor marriage from both directions. Men benefit through improved lifestyle, status, and access to sex. Women benefit through improved lifestyle, economic opportunity, and status in the social hierarchy.
Given that the selection pool for potential partners is limited, mostly to the local Amish community, or occasionally another Amish community if there’s some interaction through family ties or social events, assortative mating is the norm. Young people can be choosy, sure. But they already know most of the people in their potential mating pool, and have probably known those people for most of their lives. They have a pretty good idea how desirable they are to potential partners, and the girls especially have to think long and hard about turning down a suitor. Men are always the initiators of a relationship, and the risk of turning down an eligible man and then never getting another offer, ending up as a dreaded old maid, is always lurking in the back of their minds.
Besides that, both men and women have multiple ways to improve their spouse’s life. Women are much more than just sexual objects. Their domestic role actually raises their husband’s standard of living significantly, in a way he can’t access as a single man. And men are all valuable to women, both for resources and for status as a wife and mother. Even a very average husband or wife is a massive lifestyle boost over remaining single.
By now it should be pretty clear why marriage is almost universal among the Amish, and marriage at what most would consider a young age (19-23) is more common than not. And I haven’t even mentioned any religious teaching, because frankly I don’t think that’s a major force on an individual level. The religious beliefs shape the social and material landscape, and that landscape provides the practical incentives that cause people to make the choices they do. The fact that an Amish interpretation of the Bible encourages marriage and children is one layer removed from the reasons individual 20-year-old Amish men and women choose to get married.
I pointed out earlier that getting married and having a high birthrate, or even getting married young and having a high birthrate, are not exactly the same thing. Plenty of married couples today have one, two, or even no children, even if they got married young enough to have ten if they chose to do so. So why are the Amish different?
There’s the too-obvious answer: they don’t allow the use of contraceptives. Occam’s razor and all, but it deserves a bit more explanation. After all, the Catholic Church doesn’t allow the use of contraceptives either, and look how well that’s working out for them. Of course the enforcement mechanism doesn’t have the teeth among Catholics that it has among the Amish, but that’s not the whole story. If they were motivated enough, there’d be a way to space the children out more, maybe end up without quite so many, without anyone knowing. That doesn’t happen, because the contraceptive ban is a dead letter when couples want to have as many children as possible, which the Amish typically do.
Again, I’ll go back to incentives. What are the incentives to have children specifically, as many as possible, and not just get married and “plan for a family one day”?
For one, status. For both men and women, a large family is a marker of high status. Parents are respected and honored for doing a good job of raising well-adjusted children.
Children are also less of a financial burden for the Amish. Their children are raised well, but not in a financially intensive way that’s become expected today. They don’t have to buy a new car or SUV to fit the family, they don’t buy every child a boatload of expensive electronic gadgets every birthday and Christmas, they don’t have to pay for frequent vacations or college tuition, and they don’t have to eat out or pay for takeout or pay for childcare or a house cleaner since the wife is handling all those domestic roles herself. And the Amish don’t practice helicopter parenting, so children are much more free to play and amuse themselves without constant supervision from their parents. They don’t have to be driven to 17 different weekly structured activities. They have a farm to play on and shelves full of books to read and some toys to play with if the weather is bad, and that’s about it. And of course as the family grows, the older siblings do a large percentage of the housework and help with the younger children.
The older teenagers that are working outside the home typically give their earnings to their parents, but this basically offsets the cost of raising them, so it isn’t really an incentive to have larger families, just the removal of a disincentive.
The strongest real incentive, other than increased status and cultural inertia, that I observe for large families is that the children are the parents’ retirement plan. The Amish don’t work at jobs that offer pensions or benefits. They are exempt from paying into, but also ineligible to receive, Social Security benefits. The Social Security exemption was granted on the basis that the Amish don’t need government payments to support them in old age, because the family and community will do that. And they do.
How does this work out in practice? First, the Amish don’t practice “retirement” the way most people think of it. They teach that work is honorable and every able-bodied man should work to support his family and to help those in need. So as long as a man is physically able to work, he’ll be employed and supporting himself and his wife. And Amish women move directly from the role of mother to the role of grandmother. It’s not at all uncommon, in fact, for a woman’s first grandchild to be born before her last child is born. So plenty of Amish children are an aunt or uncle at birth, and have a niece or nephew older than they are. Grandmothers are extremely involved in helping their daughters and daughters-in-law with childcare, so they don’t often have a big stretch of free time after their children grow up and move out. And besides that, there are still the significant household responsibilities to attend to.
As a couple gets older and perhaps less able to handle everything on their own, they often move to the home of one of their grown children. Typically not into the home directly, but into what’s called a “dody haus” (grandpa house) which might be a small detached house on the same property, or a separate wing of the larger house, like an in-law suite. Here they’re able to live independently, help care for the grandchildren next door, and still be nearby so their children and grandchildren can give any care they may need in old age. If the couple has an unmarried “old maid” daughter, she’ll typically still be living with them and will be the primary caregiver.
If someone doesn’t have children to care for them, the Amish community will find a way to care for them. Some more distant relative or maybe surviving siblings will step in to help. But the expectation and the rule is that your children and grandchildren will care for you after you’re no longer able to care for yourself. Finding yourself growing old without family is an unfortunate and unpleasant situation, regardless how much the community may try to fill that role. Just as throughout earlier stages of life, social functions and social status revolve around children and family, and anyone without them will be incomplete as a person, something of an inevitable outsider to the joys of life. The best insurance against a lonely and uncomfortable old age is a large family, among which there are certain to be sufficient resources to care for you. Many elderly Amish people die with well over a hundred grandchildren and great-grandchildren, and spend their later years constantly surrounded by children and young people who deeply appreciate and respect them. Being taught and shown that respect toward their own grandparents from a young age is a strong incentive to aspire to the same status one day.
I’m not sure exactly where this fits, but I should point out somewhere that the Amish have an absolutely zero tolerance policy toward divorce. There are no legitimate grounds for divorce whatsoever, and anyone who initiates a divorce will be excommunicated from the church and shunned. If an Amish person’s spouse initiates divorce proceedings, they won’t cooperate with those proceedings in any way. If the divorce happens through the legal system without their consent anyway, they can remain a church member in good standing only by staying celibate as long as their spouse remains alive. The only acceptable second marriage is in the case of the death of a spouse. In those cases, a quick remarriage is the rule among widows and widowers with young children, since raising a family is seen as a job for a married couple, not a single person.
It’s hard to say exactly how this stance against divorce influences marriage and fertility. But it certainly limits exposure to the idea of divorce as a “solution” to marriage difficulties, and incentivizes couples to work things out for their own life satisfaction. And it dramatically reduces the financial risks men face in the modern marriage system, where the potential to lose not only their family, but also a significant portion of their material wealth, raises strong disincentives to marriage. The physical realities of married life versus single life in a more low-tech environment probably discourage divorce, but the added threat of complete social and familial ostracization eliminate it almost entirely.
Conclusion
This article is my attempt to provide some insight into the Amish culture that might help us understand the factors causing their unusually high fertility rate. I’ve titled it as part one, because I plan to follow up with some of my personal opinions on how these insights relate to the broader society. I think a lot of the proposed causes of and solutions to the global demographic collapse are completely incorrect, and my opinion is based heavily on my observation of Amish culture. That will be the focus of part two of this article.
Feel free to comment and post questions. My biggest challenge in writing this article is the fact that I take my familiarity with Amish culture for granted to some degree, so I struggled to choose which points are relevant to understanding the culture for an outsider. I’m sure I skipped over plenty of important details that may leave readers feeling confused, so I’ll do my best to answer any questions you post, and update the article with pertinent information I missed.
-
-
 @ c1d77557:bf04ec8b
2025-05-24 05:01:11
@ c1d77557:bf04ec8b
2025-05-24 05:01:11Se você está em busca de uma experiência de jogo dinâmica e diversificada, o 59h é a plataforma que você precisa conhecer. Com um foco claro na satisfação dos jogadores, ela oferece uma ampla variedade de opções de entretenimento, além de uma interface amigável e segura. Neste artigo, vamos explorar a plataforma 59h, destacando suas principais funcionalidades, jogos emocionantes e a experiência do usuário.
O Que é a Plataforma 59h? O 59h é uma plataforma inovadora que oferece uma vasta gama de jogos e experiências digitais para os entusiastas do entretenimento online. A plataforma se destaca pela sua interface intuitiva, que permite aos jogadores navegar com facilidade entre as diferentes categorias de jogos. Ela é ideal para quem busca uma experiência divertida e acessível, sem complicações.
Desde o momento em que você acessa o 59h, fica evidente o compromisso com a qualidade. A plataforma é projetada para ser acessível em diversos dispositivos, seja no seu computador, tablet ou smartphone. Isso garante que os jogadores possam aproveitar seus jogos favoritos a qualquer momento e em qualquer lugar, com a mesma qualidade e desempenho.
Uma Grande Variedade de Jogos para Todos os Gostos O 59h se destaca por sua impressionante variedade de jogos. Independentemente do tipo de jogo que você prefere, certamente encontrará algo que se adapte ao seu estilo. A plataforma oferece desde jogos de habilidade, até opções mais relaxantes e divertidas para aqueles que buscam algo mais descontraído.
Entre as opções mais populares, destacam-se os jogos de mesa, onde os jogadores podem testar suas habilidades em jogos como pôquer, blackjack e outros. Para quem prefere algo mais voltado para a sorte, o 59h também oferece jogos com elementos de sorte que podem garantir grandes recompensas.
Além disso, a plataforma está sempre atualizando seu portfólio de jogos, trazendo novidades para os jogadores. Isso significa que você nunca ficará entediado, já que sempre haverá algo novo e emocionante para experimentar.
A Experiência do Jogador no 59h Uma das maiores qualidades da plataforma 59h é sua atenção à experiência do usuário. Desde o processo de registro até a escolha de um jogo, tudo foi pensado para garantir uma navegação tranquila e sem estresse.
A plataforma é completamente segura, oferecendo métodos de pagamento rápidos e confiáveis. Isso significa que os jogadores podem depositar e retirar seus fundos com confiança, sem se preocupar com a segurança de suas informações pessoais. Além disso, o suporte ao cliente está sempre disponível para ajudar em caso de dúvidas ou problemas, garantindo que sua experiência seja o mais fluida possível.
Outro ponto que merece destaque é a comunidade de jogadores. A interação com outros jogadores é uma parte importante da plataforma, permitindo que você compartilhe dicas, participe de torneios e crie amizades. A plataforma 59h se esforça para criar um ambiente amigável e inclusivo, onde todos podem se divertir e aprender uns com os outros.
Acessibilidade e Facilidade de Uso O 59h não é apenas sobre a diversidade de jogos; também se trata de tornar o acesso o mais simples possível. A plataforma oferece um design responsivo, que se adapta perfeitamente a qualquer tipo de dispositivo. Isso significa que você pode jogar no computador, smartphone ou tablet com a mesma facilidade.
O processo de cadastro é simples e rápido, permitindo que você comece a jogar em questão de minutos. Além disso, a plataforma oferece uma série de recursos adicionais, como promoções e bônus exclusivos, que tornam a experiência ainda mais empolgante.
Conclusão O 59h se posiciona como uma plataforma de entretenimento online completa, oferecendo uma vasta gama de jogos, uma experiência de usuário de alta qualidade e um ambiente seguro e amigável para jogadores de todos os níveis. Se você procura uma plataforma confiável, diversificada e divertida, o 59h é a escolha ideal. Não importa se você é um iniciante ou um jogador experiente, há sempre algo novo para descobrir e aproveitar no 59h.
-
 @ d360efec:14907b5f
2025-05-12 04:01:23
@ d360efec:14907b5f
2025-05-12 04:01:23 -
 @ b83a28b7:35919450
2025-05-16 19:23:58
@ b83a28b7:35919450
2025-05-16 19:23:58This article was originally part of the sermon of Plebchain Radio Episode 110 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ 87e98bb6:8d6616f4
2025-05-23 15:36:32
@ 87e98bb6:8d6616f4
2025-05-23 15:36:32Use this guide if you want to keep your NixOS on the stable branch, but enable unstable application packages. It took me a while to figure out how to do this, so I wanted to share because it ended up being far easier than most of the vague explanations online made it seem.
I put a sample configuration.nix file at the very bottom to help it make more sense for new users. Remember to keep a backup of your config file, just in case!
If there are any errors please let me know. I am currently running NixOS 24.11.
Steps listed in this guide: 1. Add the unstable channel to NixOS as a secondary channel. 2. Edit the configuration.nix to enable unstable applications. 3. Add "unstable." in front of the application names in the config file (example: unstable.program). This enables the install of unstable versions during the build. 4. Rebuild.
Step 1:
- Open the console. (If you want to see which channels you currently have, type: sudo nix-channel --list)
- Add the unstable channel, type: sudo nix-channel --add https://channels.nixos.org/nixpkgs-unstable unstable
- To update the channels (bring in the possible apps), type: sudo nix-channel --update
More info here: https://nixos.wiki/wiki/Nix_channels
Step 2:
Edit your configuration.nix and add the following around your current config:
``` { config, pkgs, lib, ... }:
let unstable = import
{ config = { allowUnfree = true; }; }; in { #insert normal configuration text here } #remember to close the bracket!```
At this point it would be good to save your config and try a rebuild to make sure there are no errors. If you have errors, make sure your brackets are in the right places and/or not missing. This step will make for less troubleshooting later on if something happens to be in the wrong spot!
Step 3:
Add "unstable." to the start of each application you want to use the unstable version. (Example: unstable.brave)
Step 4:
Rebuild your config, type: sudo nixos-rebuild switch
Example configuration.nix file:
```
Config file for NixOS
{ config, pkgs, lib, ... }:
Enable unstable apps from Nix repository.
let unstable = import
{ config = { allowUnfree = true; }; }; in { #Put your normal config entries here in between the tags. Below is what your applications list needs to look like.
environment.systemPackages = with pkgs; [ appimage-run blender unstable.brave #Just add unstable. before the application name to enable the unstable version. chirp discord ];
} # Don't forget to close bracket at the end of the config file!
``` That should be all. Hope it helps.
-
 @ 3f770d65:7a745b24
2025-01-12 21:03:36
@ 3f770d65:7a745b24
2025-01-12 21:03:36I’ve been using Notedeck for several months, starting with its extremely early and experimental alpha versions, all the way to its current, more stable alpha releases. The journey has been fascinating, as I’ve had the privilege of watching it evolve from a concept into a functional and promising tool.
In its earliest stages, Notedeck was raw—offering glimpses of its potential but still far from practical for daily use. Even then, the vision behind it was clear: a platform designed to redefine how we interact with Nostr by offering flexibility and power for all users.
I'm very bullish on Notedeck. Why? Because Will Casarin is making it! Duh! 😂
Seriously though, if we’re reimagining the web and rebuilding portions of the Internet, it’s important to recognize the potential of Notedeck. If Nostr is reimagining the web, then Notedeck is reimagining the Nostr client.
Notedeck isn’t just another Nostr app—it’s more a Nostr browser that functions more like an operating system with micro-apps. How cool is that?
Much like how Google's Chrome evolved from being a web browser with a task manager into ChromeOS, a full blown operating system, Notedeck aims to transform how we interact with the Nostr. It goes beyond individual apps, offering a foundation for a fully integrated ecosystem built around Nostr.
As a Nostr evangelist, I love to scream INTEROPERABILITY and tout every application's integrations. Well, Notedeck has the potential to be one of the best platforms to showcase these integrations in entirely new and exciting ways.
Do you want an Olas feed of images? Add the media column.
Do you want a feed of live video events? Add the zap.stream column.
Do you want Nostr Nests or audio chats? Add that column to your Notedeck.
Git? Email? Books? Chat and DMs? It's all possible.
Not everyone wants a super app though, and that’s okay. As with most things in the Nostr ecosystem, flexibility is key. Notedeck gives users the freedom to choose how they engage with it—whether it’s simply following hashtags or managing straightforward feeds. You'll be able to tailor Notedeck to fit your needs, using it as extensively or minimally as you prefer.
Notedeck is designed with a local-first approach, utilizing Nostr content stored directly on your device via the local nostrdb. This will enable a plethora of advanced tools such as search and filtering, the creation of custom feeds, and the ability to develop personalized algorithms across multiple Notedeck micro-applications—all with unparalleled flexibility.
Notedeck also supports multicast. Let's geek out for a second. Multicast is a method of communication where data is sent from one source to multiple destinations simultaneously, but only to devices that wish to receive the data. Unlike broadcast, which sends data to all devices on a network, multicast targets specific receivers, reducing network traffic. This is commonly used for efficient data distribution in scenarios like streaming, conferencing, or large-scale data synchronization between devices.
In a local first world where each device holds local copies of your nostr nodes, and each device transparently syncs with each other on the local network, each node becomes a backup. Your data becomes antifragile automatically. When a node goes down it can resync and recover from other nodes. Even if not all nodes have a complete collection, negentropy can pull down only what is needed from each device. All this can be done without internet.
-Will Casarin
In the context of Notedeck, multicast would allow multiple devices to sync their Nostr nodes with each other over a local network without needing an internet connection. Wild.
Notedeck aims to offer full customization too, including the ability to design and share custom skins, much like Winamp. Users will also be able to create personalized columns and, in the future, share their setups with others. This opens the door for power users to craft tailored Nostr experiences, leveraging their expertise in the protocol and applications. By sharing these configurations as "Starter Decks," they can simplify onboarding and showcase the best of Nostr’s ecosystem.
Nostr’s “Other Stuff” can often be difficult to discover, use, or understand. Many users doesn't understand or know how to use web browser extensions to login to applications. Let's not even get started with nsecbunkers. Notedeck will address this challenge by providing a native experience that brings these lesser-known applications, tools, and content into a user-friendly and accessible interface, making exploration seamless. However, that doesn't mean Notedeck should disregard power users that want to use nsecbunkers though - hint hint.
For anyone interested in watching Nostr be developed live, right before your very eyes, Notedeck’s progress serves as a reminder of what’s possible when innovation meets dedication. The current alpha is already demonstrating its ability to handle complex use cases, and I’m excited to see how it continues to grow as it moves toward a full release later this year.
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-24 15:06:32
@ 5d4b6c8d:8a1c1ee3
2025-05-24 15:06:32I was just updating our potential points, now that we know who won MVP, who made All NBA 1st team, and which teams are still alive for the title, and it turns out that no matter who wins the title @gnilma will win this contest.
Congratulations, @gnilma!
This is just further proof that @gnilma is our NBA Guru.
Let me know where you want your 7k in winnings sent.
https://stacker.news/items/988245
-
 @ 3bf0c63f:aefa459d
2024-05-24 12:31:40
@ 3bf0c63f:aefa459d
2024-05-24 12:31:40About Nostr, email and subscriptions
I check my emails like once or twice a week, always when I am looking for something specific in there.
Then I go there and I see a bunch of other stuff I had no idea I was missing. Even many things I wish I had seen before actually. And sometimes people just expect and assume I would have checked emails instantly as they arrived.
It's so weird because I'm not making a point, I just don't remember to open the damn "gmail.com" URL.
I remember some people were making some a Nostr service a while ago that sent a DM to people with Nostr articles inside -- or some other forms of "subscription services on Nostr". It makes no sense at all.
Pulling in DMs from relays is exactly the same process (actually slightly more convoluted) than pulling normal public events, so why would a service assume that "sending a DM" was more likely to reach the target subscriber when the target had explicitly subscribed to that topic or writer?
Maybe due to how some specific clients work that is true, but fundamentally it is a very broken assumption that comes from some fantastic past era in which emails were 100% always seen and there was no way for anyone to subscribe to someone else's posts.
Building around such broken assumptions is the wrong approach. Instead we should be building new flows for subscribing to specific content from specific Nostr-native sources (creators directly or manual or automated curation providers, communities, relays etc), which is essentially what most clients are already doing anyway, but specifically Coracle's new custom feeds come to mind now.
This also reminds me of the interviewer asking the Farcaster creator if Farcaster made "email addresses available to content creators" completely ignoring all the cryptography and nature of the protocol (Farcaster is shit, but at least they tried, and in this example you could imagine the interviewer asking the same thing about Nostr).
I imagine that if the interviewer had asked these people who were working (or suggesting) the Nostr DM subscription flow they would have answered: "no, you don't get their email addresses, but you can send them uncensorable DMs!" -- and that, again, is getting everything backwards.
-
 @ 70c48e4b:00ce3ccb
2025-05-21 10:52:12
@ 70c48e4b:00ce3ccb
2025-05-21 10:52:12Dear readers,
“The direct use of force is such a poor solution to any problem, it is generally employed only by small children and large nations.” — David Friedman
What If we could enforce promises without force?
David Friedman, in his book The Machinery of Freedom, tosses out a pretty wild idea: that people can build systems of cooperation and justice without needing a government at all. These systems rely on voluntary agreements, social reputation, and mutual incentives. In such a world, contracts hold value because honoring a promise brings greater rewards than breaking it.
From Friedman to Bitcoin
https://i.ytimg.com/vi/e8zsFTV94bw/maxresdefault.jpg
This vision shaped the thinking behind Angor, a funding tool built on Bitcoin. Friedman’s ideas showed that systems of cooperation could work without central authority, and Bitcoin now provides the foundation to build them. It records transactions in a public and tamper-proof way. With features like Taproot, people can set clear rules for funding and accountability. Angor uses these tools to help founders and backers create agreements that are transparent and easy to verify.
The result is a new kind of marketplace where follow-through is visible, and reputation becomes a real asset. Instead of relying on enforcement from above, trust is earned through action and built into the system itself.
What happens after the project succeeds?
One important question kept returning throughout our work: what happens after a project succeeds? The founder raises the funds, delivers the product, and begins earning revenue. What mechanism ensures that revenue is shared as promised? How can investors protect their interests in an environment that relies on voluntary structure rather than external authority?
To explore possible answers, we looked at how libertarian thinkers approach contracts in stateless systems.
How libertarian thinkers approach contracts without the state?
Friedman, along with other libertarian thinkers like Murray Rothbard and Bruce Benson, describes voluntarily created legal systems where people make binding agreements and use private mechanisms to enforce them. These mechanisms include:
• Reputational risk • Collateralized performance • Community arbitration • Decentralized insuranceSuch tools can replace state-backed enforcement when trust is earned and incentives are aligned.
If founders are anonymous:
When a founder chooses to remain pseudonymous, legal enforcement is not available. In this case, the agreement between the founder and investor can rely on cryptographic mechanisms such as performance bonds, revenue proofs, and public reputation systems.
- Performance Bonds
• Founders deposit additional Bitcoin into a separate, time-locked contract. As they meet revenue-sharing milestones, they are allowed to unlock specific portions of this bond.
• If a revenue allocation is missed or a deadline passes without fulfillment, the contract redirects the bond to investors through a Taproot clause i.e. a feature in Bitcoin that lets you set up ‘if-this-then-that’ rules directly into a transaction, but privately. This creates a clear and automatic consequence, reinforcing accountability through financial incentives.
- Revenue Proofs and Oracles
• Most founders, especially those running small businesses like cafes, games, or services, do not earn revenue in Bitcoin. Their income flows through fiat systems, which means automatic on-chain revenue streaming is not an option. The only way to maintain transparency is to prove income after the fact. This starts with exporting a sales report from a platform such as Stripe, Revolut, or a point-of-sale system. The founder hashes the file and posts that hash to the Bitcoin blockchain as a timestamped public reference.
• An oracle plays the role of a neutral verifier. This could be a trusted accountant or an observer chosen by the investor community. Their job is simple: compare the actual report with the hash recorded on-chain. If the data matches, the oracle signs a message that triggers the revenue-share payout using a Discreet Log Contract (DLC).
A DLC is similar to a smart contract, but built for Bitcoin. It allows two parties to agree on a specific outcome, such as how much revenue was made, and only releases funds when that outcome is confirmed by the oracle.
This process does not depend on central enforcement. Instead, it works through mutual agreement and the oracle’s reputation, or any collateral they may have provided in advance.
- Reputation as collateral
• Every revenue-share payout is recorded on the Bitcoin blockchain, making it publicly visible and verifiable. Community-run indexers can scan the chain and track whether a founder consistently delivers payments on time. This performance history is then summarized into what is known as a “contract streak,” which refers to the number of consecutive payouts completed without delay.
• These streaks are published as signed events through protocols like Nostr, allowing anyone to verify a founder’s track record. A strong, uninterrupted streak builds credibility and can improve the chances of raising funds for future projects. In contrast, a broken streak signals risk, which discourages new investment and reduces access to support from the Angor community.
If founders are public:
When a founder uses a real identity, the parties can combine legal agreements with on-chain contracts. These hybrid arrangements allow for tools like enforceable smart contracts, voluntary arbitration, and potentially community-backed insurance.
- Legally binding smart contracts
• This type of agreement formally identifies the founder’s legal entity and clearly links it to specific Taproot addresses used in the project. It outlines the rules for revenue sharing, describes what constitutes a breach, and specifies how disputes should be resolved. Because it is a formal legal document, it can be enforced in any relevant jurisdiction where the founder has a presence or assets.
- Private arbitration
• During the contract setup, both parties can agree to a neutral arbitrator who will step in if a dispute arises. If a revenue payout is delayed or missed, the arbitrator reviews all relevant data, including on-chain records, oracle confirmations, and supporting documentation. Based on this evidence, the arbitrator issues a decision that determines whether funds should be released, held, or redirected. This method provides a clear resolution process without involving courts, while still maintaining a fair and structured outcome.
- Equity sharing and traditional securities
• When founders are publicly identified and operating under a registered entity, they can also offer equity in the company as part of the funding arrangement. This can take the form of direct share issuance, convertible notes, or tokenized equity, depending on jurisdictional frameworks and investor preferences.
While Angor does not facilitate equity transfers directly, the on-chain agreement can reference these arrangements clearly. Investors may receive shares documented in a cap table, with accompanying legal agreements that govern dividend rights, voting power, or exit terms.
This method provides a more conventional form of investor alignment and is often well-understood by experienced backers. It can also be combined with on-chain revenue-sharing mechanisms to create hybrid models that balance transparency with long-term equity value.
Final Thought: Alignment Over Authority
The ideas in The Machinery of Freedom show how people can build cooperative systems without relying on centralized authority. Angor puts those ideas into action by applying them to decentralized crowdfunding. Each campaign becomes a contract. Each payout becomes a public signal of integrity. Reputation is built over time, through visible and verifiable performance.
This approach shifts enforcement from force to alignment. It rewards honesty and transparency while making misuse costly. By designing systems where trust is earned through action and recorded on-chain, we move toward a more resilient model of funding. This model is grounded in consent, shaped by shared incentives, and supported by the open logic of Bitcoin.
Bitcoin itself works this way. Miners follow the rules not because they are told to, but because breaking them wastes energy, time, and opportunity. The cost of cheating is built into the system. Angor adopts the same principle: integrity is not enforced from above, it is embedded in the architecture.
If you are building on Angor or exploring similar ideas, reach out. The tools are evolving, and the community is growing.
https://docs.angor.io/images/tools/hub.png
Have you tried Angor yet?
Thank you & Ciao. Guest writer: Paco nostr:npub1v67clmf4jrezn8hsz28434nc0y5fu65e5esws04djnl2kasxl5tskjmjjk
-
 @ 3bf0c63f:aefa459d
2024-05-21 12:38:08
@ 3bf0c63f:aefa459d
2024-05-21 12:38:08Bitcoin transactions explained
A transaction is a piece of data that takes inputs and produces outputs. Forget about the blockchain thing, Bitcoin is actually just a big tree of transactions. The blockchain is just a way to keep transactions ordered.
Imagine you have 10 satoshis. That means you have them in an unspent transaction output (UTXO). You want to spend them, so you create a transaction. The transaction should reference unspent outputs as its inputs. Every transaction has an immutable id, so you use that id plus the index of the output (because transactions can have multiple outputs). Then you specify a script that unlocks that transaction and related signatures, then you specify outputs along with a script that locks these outputs.

As you can see, there's this lock/unlocking thing and there are inputs and outputs. Inputs must be unlocked by fulfilling the conditions specified by the person who created the transaction they're in. And outputs must be locked so anyone wanting to spend those outputs will need to unlock them.
For most of the cases locking and unlocking means specifying a public key whose controller (the person who has the corresponding private key) will be able to spend. Other fancy things are possible too, but we can ignore them for now.
Back to the 10 satoshis you want to spend. Since you've successfully referenced 10 satoshis and unlocked them, now you can specify the outputs (this is all done in a single step). You can specify one output of 10 satoshis, two of 5, one of 3 and one of 7, three of 3 and so on. The sum of outputs can't be more than 10. And if the sum of outputs is less than 10 the difference goes to fees. In the first days of Bitcoin you didn't need any fees, but now you do, otherwise your transaction won't be included in any block.

If you're still interested in transactions maybe you could take a look at this small chapter of that Andreas Antonopoulos book.
If you hate Andreas Antonopoulos because he is a communist shitcoiner or don't want to read more than half a page, go here: https://en.bitcoin.it/wiki/Coin_analogy
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 3bf0c63f:aefa459d
2024-03-23 08:57:08
@ 3bf0c63f:aefa459d
2024-03-23 08:57:08Nostr is not decentralized nor censorship-resistant
Peter Todd has been saying this for a long time and all the time I've been thinking he is misunderstanding everything, but I guess a more charitable interpretation is that he is right.
Nostr today is indeed centralized.
Yesterday I published two harmless notes with the exact same content at the same time. In two minutes the notes had a noticeable difference in responses:
The top one was published to
wss://nostr.wine,wss://nos.lol,wss://pyramid.fiatjaf.com. The second was published to the relay where I generally publish all my notes to,wss://pyramid.fiatjaf.com, and that is announced on my NIP-05 file and on my NIP-65 relay list.A few minutes later I published that screenshot again in two identical notes to the same sets of relays, asking if people understood the implications. The difference in quantity of responses can still be seen today:
These results are skewed now by the fact that the two notes got rebroadcasted to multiple relays after some time, but the fundamental point remains.
What happened was that a huge lot more of people saw the first note compared to the second, and if Nostr was really censorship-resistant that shouldn't have happened at all.
Some people implied in the comments, with an air of obviousness, that publishing the note to "more relays" should have predictably resulted in more replies, which, again, shouldn't be the case if Nostr is really censorship-resistant.
What happens is that most people who engaged with the note are following me, in the sense that they have instructed their clients to fetch my notes on their behalf and present them in the UI, and clients are failing to do that despite me making it clear in multiple ways that my notes are to be found on
wss://pyramid.fiatjaf.com.If we were talking not about me, but about some public figure that was being censored by the State and got banned (or shadowbanned) by the 3 biggest public relays, the sad reality would be that the person would immediately get his reach reduced to ~10% of what they had before. This is not at all unlike what happened to dozens of personalities that were banned from the corporate social media platforms and then moved to other platforms -- how many of their original followers switched to these other platforms? Probably some small percentage close to 10%. In that sense Nostr today is similar to what we had before.
Peter Todd is right that if the way Nostr works is that you just subscribe to a small set of relays and expect to get everything from them then it tends to get very centralized very fast, and this is the reality today.
Peter Todd is wrong that Nostr is inherently centralized or that it needs a protocol change to become what it has always purported to be. He is in fact wrong today, because what is written above is not valid for all clients of today, and if we drive in the right direction we can successfully make Peter Todd be more and more wrong as time passes, instead of the contrary.
See also:
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 58537364:705b4b85
2025-05-24 03:25:05
@ 58537364:705b4b85
2025-05-24 03:25:05Ep 228 "วิชาชีวิต"
คนเราเมื่อเกิดมาแล้ว ไม่ได้หวังแค่มีชีวิตรอดเท่านั้น แต่ยังปรารถนา "ความเจริญก้าวหน้า" และ "ความสุขในชีวิต"
จึงพากันศึกษาเล่าเรียนเพื่อให้มี "วิชาความรู้" สำหรับการประกอบอาชีพ โดยเชื่อว่า การงานที่มั่นคงย่อมนำ "ความสำเร็จ" และ "ความเจริญก้าวหน้า" มาให้
อย่างไรก็ตาม...ความสำเร็จในวิชาชีพหรือความเจริญก้าวหน้าในชีวิต ไม่ได้เป็นหลักประกันความสุขอย่างแท้จริง
แม้เงินทองและทรัพย์สมบัติจะช่วยให้ชีวิตมีความสุข สะดวก สบาย แต่ไม่ได้ช่วยให้สุขใจในสิ่งที่ตนมี หากยังรู้สึกว่า "ตนยังมีไม่พอ"
ขณะเดียวกันชื่อเสียงเกียรติยศที่ได้มาก็ไม่ช่วยให้คลายความทุกข์ใจ เมื่อต้องเผชิญปัญหาต่างๆ นาๆ
ทั้งการพลัดพราก การสูญเสียบุคคลผู้เป็นที่รัก ความเจ็บป่วย และความตายที่ต้องเกิดขึ้นกับทุกคน
ยิ่งกว่านั้น...ความสำเร็จในอาชีพและความเจริญก้าวหน้าในชีวิต ล้วนเป็น "สิ่งไม่เที่ยง" แปรผันตกต่ำ ไม่สามารถควบคุมได้
วิชาชีพทั้งหลายช่วยให้เราหาเงินได้มากขึ้น แต่ไม่ได้ช่วยให้เราเข้าถึง "ความสุขที่แท้จริง"
คนที่ประสบความสำเร็จในวิชาชีพไม่น้อย ที่มีชีวิตอมทุกข์ ความเครียดรุมเร้า สุขภาพเสื่อมโทรม
หากเราไม่อยากเผชิญกับสิ่งเหล่านี้ ควรเรียน "วิชาชีวิต" เพื่อเข้าใจโลก เข้าใจชีวิต รู้เท่าทันความผันแปรไปของสรรพสิ่ง
วิชาชีวิต...เรียนจากประสบการณ์ชีวิต เมื่อมีปัญหาต่างๆ ขอให้คิดว่า คือ "บททดสอบ"
จงหมั่นศึกษาหาบทเรียนจากวิชานี้อยู่เสมอ สร้าง "ความตระหนักรู้" ถึงความสำคัญในการมีชีวิต
ช่วงที่ผ่านมา เมื่อมีปัญหาฉันไม่สามารถหาทางออกจากทุกข์ได้เศร้า เสียใจ ทุรน ทุราย สอบตก "วิชาชีวิต"
โชคดีครูบาอาจารย์ให้ข้อคิด กล่าวว่า เป็นเรื่องธรรมดาหากเรายังไม่เข้าใจชีวิต ทุกสิ่งล้วนผันแปร เกิด-ดับ เป็นธรรมดา ท่านเมตตาส่งหนังสือเล่มนี้มาให้
เมื่อค่อยๆ ศึกษา ทำความเข้าใจ นำความทุกข์ที่เกิดขึ้นมาพิจารณา เห็นว่าเมื่อ "สอบตก" ก็ "สอบใหม่" จนกว่าจะผ่านไปได้
วิชาทางโลกเมื่อสอบตกยังเปิดโอกาสให้เรา "สอบซ่อม" วิชาทางธรรมก็เช่นเดียวกัน หากเจอปัญหา อุปสรรค หรือ ความทุกข์ถาโถมเข้ามา ขอให้เราตั้งสติ ว่า จะตั้งใจทำข้อสอบนี้ให้ผ่านไปให้จงได้
หากเราสามารถดำเนินชีวิตด้วยความเข้าใจ เราจะค้นพบ "วิชาชีวิต" ที่สามารถทำให้หลุดพ้นจากความทุกข์ได้แน่นอน
ด้วยรักและปรารถนาดี ปาริชาติ รักตะบุตร 21 เมษายน 2566
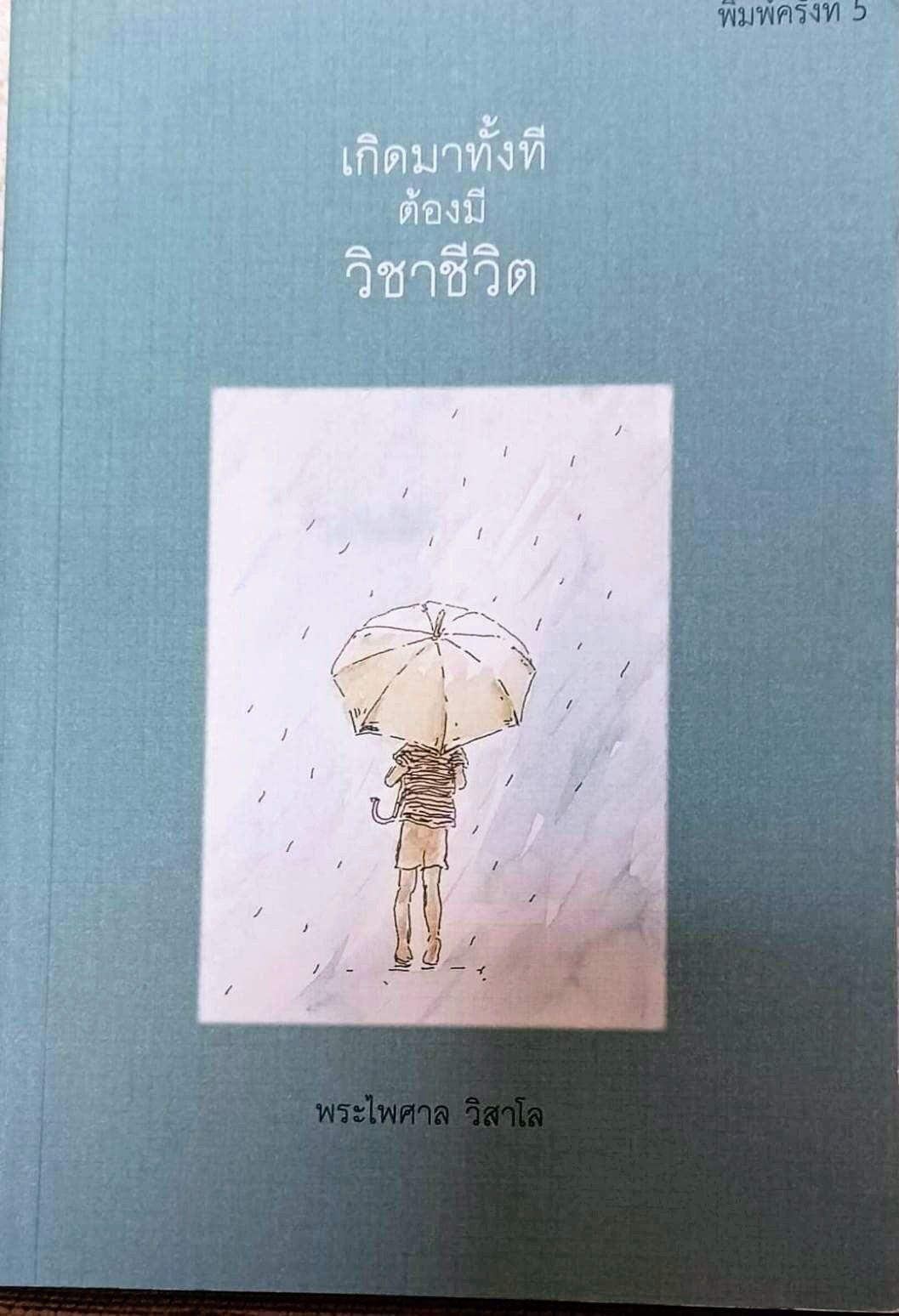
น้อมกราบขอบพระคุณพระ อ.ไพศาล วิสาโล เป็นอย่างสูง ที่ท่านเมตตา ให้ข้อธรรมะยามทุกข์ใจและส่งหนังสือมาให้ จึงตั้งใจอยากแบ่งปันเป็นธรรมทาน
-
 @ 0e9491aa:ef2adadf
2025-05-24 14:01:35
@ 0e9491aa:ef2adadf
2025-05-24 14:01:35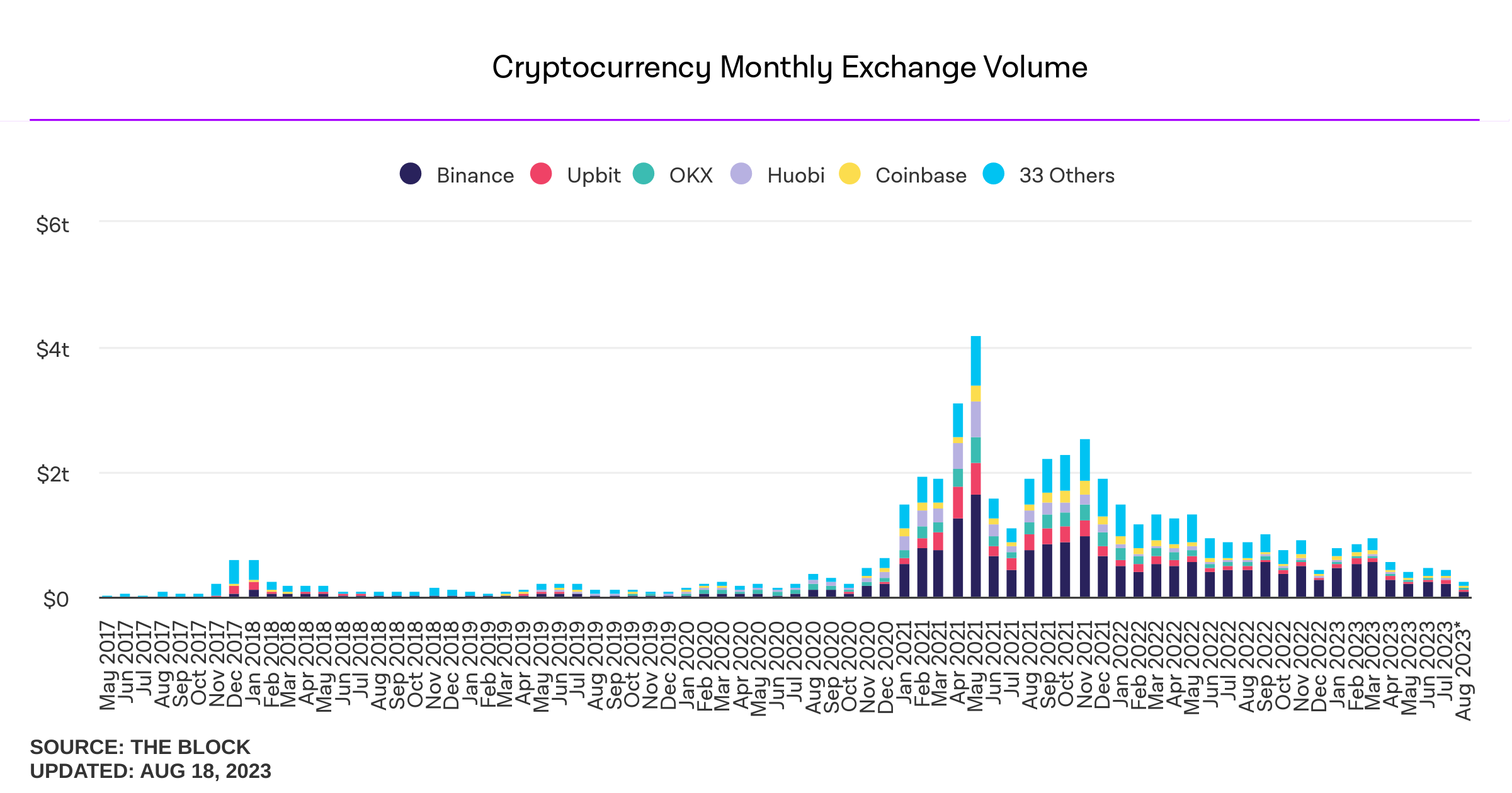
Influencers would have you believe there is an ongoing binance bank run but bitcoin wallet data says otherwise.
- binance wallets are near all time highs
- bitfinex wallets are also trending up
- gemini and coinbase are being hit with massive withdrawals thoughYou should not trust custodians, they can rug you without warning. It is incredibly important you learn how to hold bitcoin yourself, but also consider not blindly trusting influencers with a ref link to shill you.
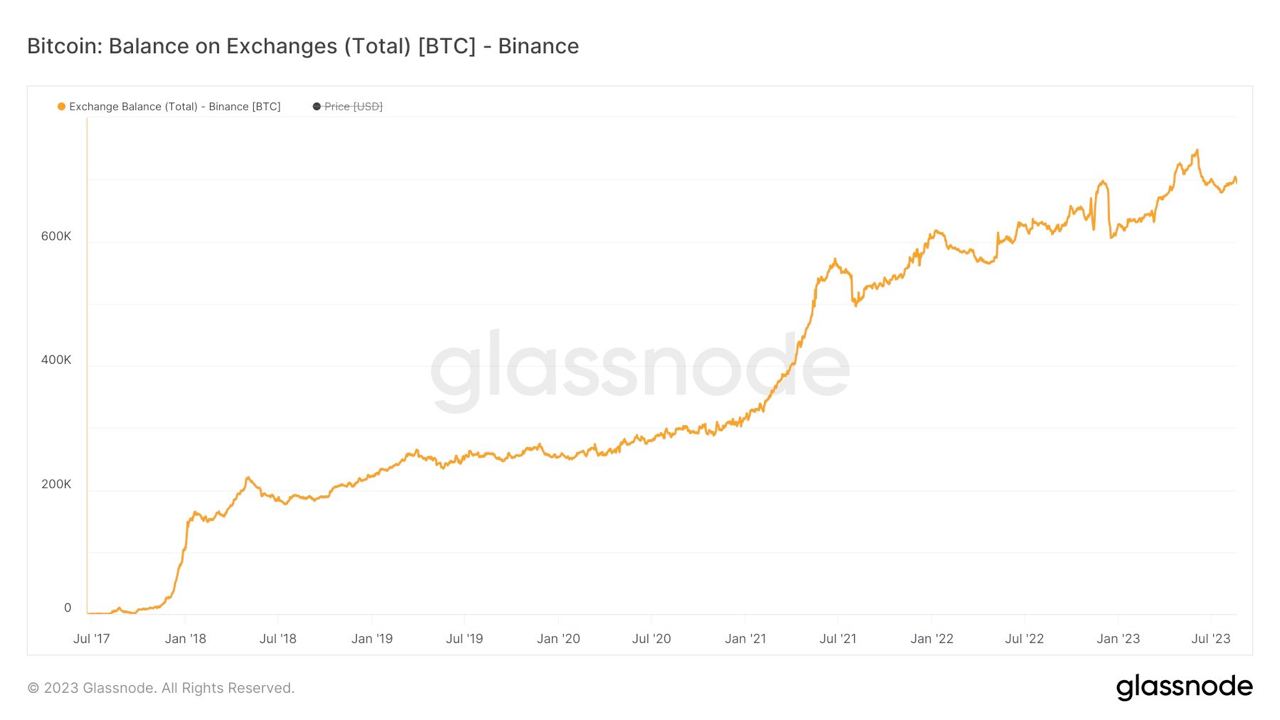
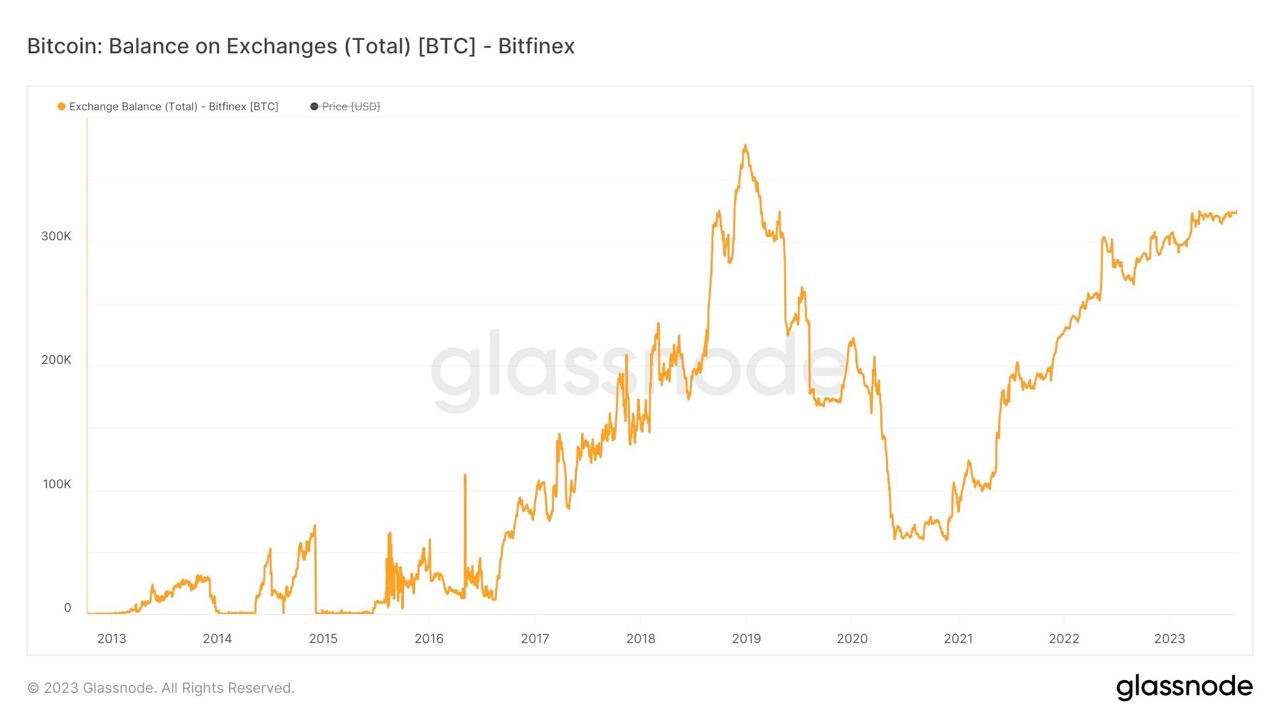
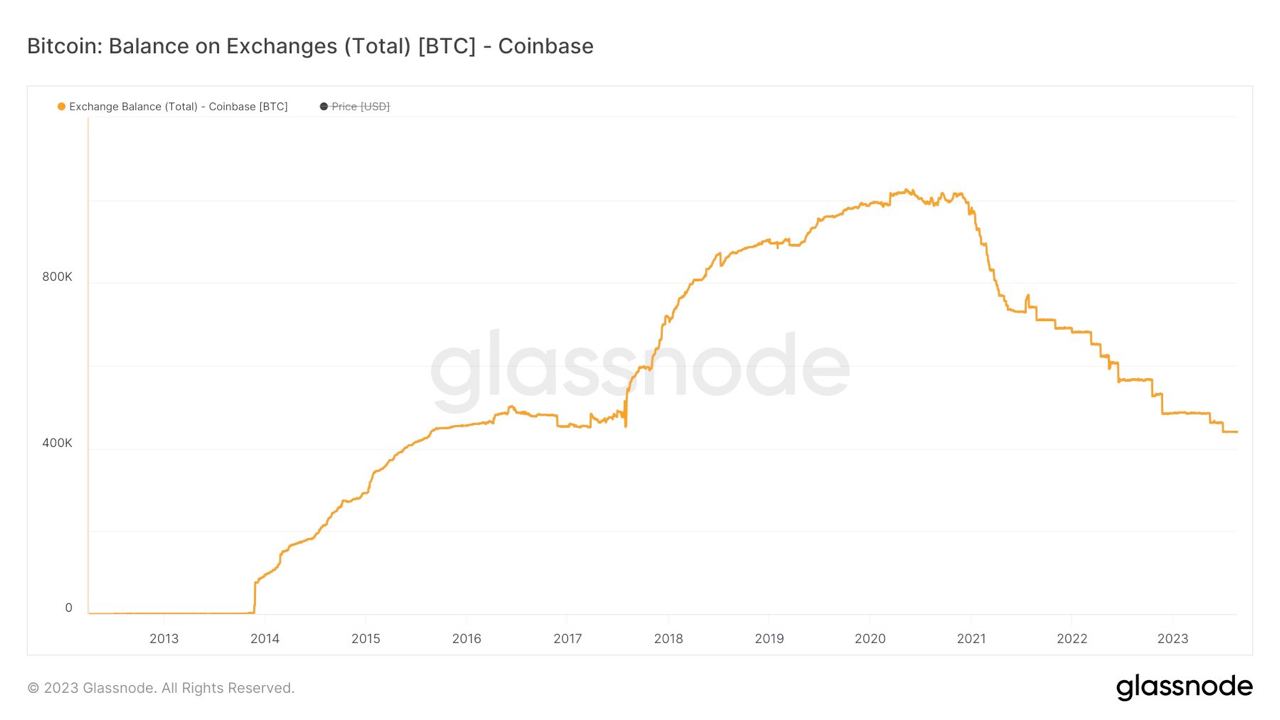

If you found this post helpful support my work with bitcoin.

-
 @ 3f770d65:7a745b24
2025-01-05 18:56:33
@ 3f770d65:7a745b24
2025-01-05 18:56:33New Year’s resolutions often feel boring and repetitive. Most revolve around getting in shape, eating healthier, or giving up alcohol. While the idea is interesting—using the start of a new calendar year as a catalyst for change—it also seems unnecessary. Why wait for a specific date to make a change? If you want to improve something in your life, you can just do it. You don’t need an excuse.
That’s why I’ve never been drawn to the idea of making a list of resolutions. If I wanted a change, I’d make it happen, without worrying about the calendar. At least, that’s how I felt until now—when, for once, the timing actually gave me a real reason to embrace the idea of New Year’s resolutions.
Enter Olas.
If you're a visual creator, you've likely experienced the relentless grind of building a following on platforms like Instagram—endless doomscrolling, ever-changing algorithms, and the constant pressure to stay relevant. But what if there was a better way? Olas is a Nostr-powered alternative to Instagram that prioritizes community, creativity, and value-for-value exchanges. It's a game changer.
Instagram’s failings are well-known. Its algorithm often dictates whose content gets seen, leaving creators frustrated and powerless. Monetization hurdles further alienate creators who are forced to meet arbitrary follower thresholds before earning anything. Additionally, the platform’s design fosters endless comparisons and exposure to negativity, which can take a significant toll on mental health.
Instagram’s algorithms are notorious for keeping users hooked, often at the cost of their mental health. I've spoken about this extensively, most recently at Nostr Valley, explaining how legacy social media is bad for you. You might find yourself scrolling through content that leaves you feeling anxious or drained. Olas takes a fresh approach, replacing "doomscrolling" with "bloomscrolling." This is a common theme across the Nostr ecosystem. The lack of addictive rage algorithms allows the focus to shift to uplifting, positive content that inspires rather than exhausts.
Monetization is another area where Olas will set itself apart. On Instagram, creators face arbitrary barriers to earning—needing thousands of followers and adhering to restrictive platform rules. Olas eliminates these hurdles by leveraging the Nostr protocol, enabling creators to earn directly through value-for-value exchanges. Fans can support their favorite artists instantly, with no delays or approvals required. The plan is to enable a brand new Olas account that can get paid instantly, with zero followers - that's wild.
Olas addresses these issues head-on. Operating on the open Nostr protocol, it removes centralized control over one's content’s reach or one's ability to monetize. With transparent, configurable algorithms, and a community that thrives on mutual support, Olas creates an environment where creators can grow and succeed without unnecessary barriers.
Join me on my New Year's resolution. Join me on Olas and take part in the #Olas365 challenge! It’s a simple yet exciting way to share your content. The challenge is straightforward: post at least one photo per day on Olas (though you’re welcome to share more!).
Download on Android or download via Zapstore.
Let's make waves together.
-
 @ d360efec:14907b5f
2025-05-10 03:57:17
@ d360efec:14907b5f
2025-05-10 03:57:17Disclaimer: * การวิเคราะห์นี้เป็นเพียงแนวทาง ไม่ใช่คำแนะนำในการซื้อขาย * การลงทุนมีความเสี่ยง ผู้ลงทุนควรตัดสินใจด้วยตนเอง
-
 @ 3bf0c63f:aefa459d
2024-03-19 14:32:01
@ 3bf0c63f:aefa459d
2024-03-19 14:32:01Censorship-resistant relay discovery in Nostr
In Nostr is not decentralized nor censorship-resistant I said Nostr is centralized. Peter Todd thinks it is centralized by design, but I disagree.
Nostr wasn't designed to be centralized. The idea was always that clients would follow people in the relays they decided to publish to, even if it was a single-user relay hosted in an island in the middle of the Pacific ocean.
But the Nostr explanations never had any guidance about how to do this, and the protocol itself never had any enforcement mechanisms for any of this (because it would be impossible).
My original idea was that clients would use some undefined combination of relay hints in reply tags and the (now defunct)
kind:2relay-recommendation events plus some form of manual action ("it looks like Bob is publishing on relay X, do you want to follow him there?") to accomplish this. With the expectation that we would have a better idea of how to properly implement all this with more experience, Branle, my first working client didn't have any of that implemented, instead it used a stupid static list of relays with read/write toggle -- although it did publish relay hints and kept track of those internally and supportedkind:2events, these things were not really useful.Gossip was the first client to implement a truly censorship-resistant relay discovery mechanism that used NIP-05 hints (originally proposed by Mike Dilger) relay hints and
kind:3relay lists, and then with the simple insight of NIP-65 that got much better. After seeing it in more concrete terms, it became simpler to reason about it and the approach got popularized as the "gossip model", then implemented in clients like Coracle and Snort.Today when people mention the "gossip model" (or "outbox model") they simply think about NIP-65 though. Which I think is ok, but too restrictive. I still think there is a place for the NIP-05 hints,
nprofileandneventrelay hints and specially relay hints in event tags. All these mechanisms are used together in ZBD Social, for example, but I believe also in the clients listed above.I don't think we should stop here, though. I think there are other ways, perhaps drastically different ways, to approach content propagation and relay discovery. I think manual action by users is underrated and could go a long way if presented in a nice UX (not conceived by people that think users are dumb animals), and who knows what. Reliance on third-parties, hardcoded values, social graph, and specially a mix of multiple approaches, is what Nostr needs to be censorship-resistant and what I hope to see in the future.
-
 @ 2b468756:7930dd9c
2025-05-23 12:41:01
@ 2b468756:7930dd9c
2025-05-23 12:41:01Agorisme is libertarisme in de praktijk: op legale wijze maximale economische en persoonlijke vrijheid. Samen ontdekken en delen we wat er allemaal mogelijk is. We doen dit door: - organiseren jaarlijks agorismefestival - organiseren meerdere themadagen / excursies per jaar - bundelen praktische kennis op Agorisme Wiki - online uitwisselen via (thema)appgroepen
Op deze site worden activiteiten aangekondigd en kun je je opgeven.
Binnenkort: - cursussen metselen, stucen en vloeren - reis naar libertarisch dorp Walden Woods en Liberstad in Noorwegen - introductie Krav Maga zelfverdediging
We zijn gelieerd aan de libertarische partij.
Graag tot ziens!
-
 @ 3bf0c63f:aefa459d
2024-01-29 02:19:25
@ 3bf0c63f:aefa459d
2024-01-29 02:19:25Nostr: a quick introduction, attempt #1
Nostr doesn't have a material existence, it is not a website or an app. Nostr is just a description what kind of messages each computer can send to the others and vice-versa. It's a very simple thing, but the fact that such description exists allows different apps to connect to different servers automatically, without people having to talk behind the scenes or sign contracts or anything like that.
When you use a Nostr client that is what happens, your client will connect to a bunch of servers, called relays, and all these relays will speak the same "language" so your client will be able to publish notes to them all and also download notes from other people.
That's basically what Nostr is: this communication layer between the client you run on your phone or desktop computer and the relay that someone else is running on some server somewhere. There is no central authority dictating who can connect to whom or even anyone who knows for sure where each note is stored.
If you think about it, Nostr is very much like the internet itself: there are millions of websites out there, and basically anyone can run a new one, and there are websites that allow you to store and publish your stuff on them.
The added benefit of Nostr is that this unified "language" that all Nostr clients speak allow them to switch very easily and cleanly between relays. So if one relay decides to ban someone that person can switch to publishing to others relays and their audience will quickly follow them there. Likewise, it becomes much easier for relays to impose any restrictions they want on their users: no relay has to uphold a moral ground of "absolute free speech": each relay can decide to delete notes or ban users for no reason, or even only store notes from a preselected set of people and no one will be entitled to complain about that.
There are some bad things about this design: on Nostr there are no guarantees that relays will have the notes you want to read or that they will store the notes you're sending to them. We can't just assume all relays will have everything — much to the contrary, as Nostr grows more relays will exist and people will tend to publishing to a small set of all the relays, so depending on the decisions each client takes when publishing and when fetching notes, users may see a different set of replies to a note, for example, and be confused.
Another problem with the idea of publishing to multiple servers is that they may be run by all sorts of malicious people that may edit your notes. Since no one wants to see garbage published under their name, Nostr fixes that by requiring notes to have a cryptographic signature. This signature is attached to the note and verified by everybody at all times, which ensures the notes weren't tampered (if any part of the note is changed even by a single character that would cause the signature to become invalid and then the note would be dropped). The fix is perfect, except for the fact that it introduces the requirement that each user must now hold this 63-character code that starts with "nsec1", which they must not reveal to anyone. Although annoying, this requirement brings another benefit: that users can automatically have the same identity in many different contexts and even use their Nostr identity to login to non-Nostr websites easily without having to rely on any third-party.
To conclude: Nostr is like the internet (or the internet of some decades ago): a little chaotic, but very open. It is better than the internet because it is structured and actions can be automated, but, like in the internet itself, nothing is guaranteed to work at all times and users many have to do some manual work from time to time to fix things. Plus, there is the cryptographic key stuff, which is painful, but cool.
-
 @ 8bf578f4:b6303c41
2025-05-23 12:11:21
@ 8bf578f4:b6303c41
2025-05-23 12:11:21tag discoverability test
testing1788
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:48
@ 04c915da:3dfbecc9
2025-05-20 15:50:48For years American bitcoin miners have argued for more efficient and free energy markets. It benefits everyone if our energy infrastructure is as efficient and robust as possible. Unfortunately, broken incentives have led to increased regulation throughout the sector, incentivizing less efficient energy sources such as solar and wind at the detriment of more efficient alternatives.
The result has been less reliable energy infrastructure for all Americans and increased energy costs across the board. This naturally has a direct impact on bitcoin miners: increased energy costs make them less competitive globally.
Bitcoin mining represents a global energy market that does not require permission to participate. Anyone can plug a mining computer into power and internet to get paid the current dynamic market price for their work in bitcoin. Using cellphone or satellite internet, these mines can be located anywhere in the world, sourcing the cheapest power available.
Absent of regulation, bitcoin mining naturally incentivizes the build out of highly efficient and robust energy infrastructure. Unfortunately that world does not exist and burdensome regulations remain the biggest threat for US based mining businesses. Jurisdictional arbitrage gives miners the option of moving to a friendlier country but that naturally comes with its own costs.
Enter AI. With the rapid development and release of AI tools comes the requirement of running massive datacenters for their models. Major tech companies are scrambling to secure machines, rack space, and cheap energy to run full suites of AI enabled tools and services. The most valuable and powerful tech companies in America have stumbled into an accidental alliance with bitcoin miners: THE NEED FOR CHEAP AND RELIABLE ENERGY.
Our government is corrupt. Money talks. These companies will push for energy freedom and it will greatly benefit us all.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 3f770d65:7a745b24
2024-12-31 17:03:46
@ 3f770d65:7a745b24
2024-12-31 17:03:46Here are my predictions for Nostr in 2025:
Decentralization: The outbox and inbox communication models, sometimes referred to as the Gossip model, will become the standard across the ecosystem. By the end of 2025, all major clients will support these models, providing seamless communication and enhanced decentralization. Clients that do not adopt outbox/inbox by then will be regarded as outdated or legacy systems.
Privacy Standards: Major clients such as Damus and Primal will move away from NIP-04 DMs, adopting more secure protocol possibilities like NIP-17 or NIP-104. These upgrades will ensure enhanced encryption and metadata protection. Additionally, NIP-104 MLS tools will drive the development of new clients and features, providing users with unprecedented control over the privacy of their communications.
Interoperability: Nostr's ecosystem will become even more interconnected. Platforms like the Olas image-sharing service will expand into prominent clients such as Primal, Damus, Coracle, and Snort, alongside existing integrations with Amethyst, Nostur, and Nostrudel. Similarly, audio and video tools like Nostr Nests and Zap.stream will gain seamless integration into major clients, enabling easy participation in live events across the ecosystem.
Adoption and Migration: Inspired by early pioneers like Fountain and Orange Pill App, more platforms will adopt Nostr for authentication, login, and social systems. In 2025, a significant migration from a high-profile application platform with hundreds of thousands of users will transpire, doubling Nostr’s daily activity and establishing it as a cornerstone of decentralized technologies.
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ 3bf0c63f:aefa459d
2024-01-15 11:15:06
@ 3bf0c63f:aefa459d
2024-01-15 11:15:06Pequenos problemas que o Estado cria para a sociedade e que não são sempre lembrados
- **vale-transporte**: transferir o custo com o transporte do funcionário para um terceiro o estimula a morar longe de onde trabalha, já que morar perto é normalmente mais caro e a economia com transporte é inexistente. - **atestado médico**: o direito a faltar o trabalho com atestado médico cria a exigência desse atestado para todas as situações, substituindo o livre acordo entre patrão e empregado e sobrecarregando os médicos e postos de saúde com visitas desnecessárias de assalariados resfriados. - **prisões**: com dinheiro mal-administrado, burocracia e péssima alocação de recursos -- problemas que empresas privadas em competição (ou mesmo sem qualquer competição) saberiam resolver muito melhor -- o Estado fica sem presídios, com os poucos existentes entupidos, muito acima de sua alocação máxima, e com isto, segundo a bizarra corrente de responsabilidades que culpa o juiz que condenou o criminoso por sua morte na cadeia, juízes deixam de condenar à prisão os bandidos, soltando-os na rua. - **justiça**: entrar com processos é grátis e isto faz proliferar a atividade dos advogados que se dedicam a criar problemas judiciais onde não seria necessário e a entupir os tribunais, impedindo-os de fazer o que mais deveriam fazer. - **justiça**: como a justiça só obedece às leis e ignora acordos pessoais, escritos ou não, as pessoas não fazem acordos, recorrem sempre à justiça estatal, e entopem-na de assuntos que seriam muito melhor resolvidos entre vizinhos. - **leis civis**: as leis criadas pelos parlamentares ignoram os costumes da sociedade e são um incentivo a que as pessoas não respeitem nem criem normas sociais -- que seriam maneiras mais rápidas, baratas e satisfatórias de resolver problemas. - **leis de trãnsito**: quanto mais leis de trânsito, mais serviço de fiscalização são delegados aos policiais, que deixam de combater crimes por isto (afinal de contas, eles não querem de fato arriscar suas vidas combatendo o crime, a fiscalização é uma excelente desculpa para se esquivarem a esta responsabilidade). - **financiamento educacional**: é uma espécie de subsídio às faculdades privadas que faz com que se criem cursos e mais cursos que são cada vez menos recheados de algum conhecimento ou técnica útil e cada vez mais inúteis. - **leis de tombamento**: são um incentivo a que o dono de qualquer área ou construção "histórica" destrua todo e qualquer vestígio de história que houver nele antes que as autoridades descubram, o que poderia não acontecer se ele pudesse, por exemplo, usar, mostrar e se beneficiar da história daquele local sem correr o risco de perder, de fato, a sua propriedade. - **zoneamento urbano**: torna as cidades mais espalhadas, criando uma necessidade gigantesca de carros, ônibus e outros meios de transporte para as pessoas se locomoverem das zonas de moradia para as zonas de trabalho. - **zoneamento urbano**: faz com que as pessoas percam horas no trânsito todos os dias, o que é, além de um desperdício, um atentado contra a sua saúde, que estaria muito melhor servida numa caminhada diária entre a casa e o trabalho. - **zoneamento urbano**: torna ruas e as casas menos seguras criando zonas enormes, tanto de residências quanto de indústrias, onde não há movimento de gente alguma. - **escola obrigatória + currículo escolar nacional**: emburrece todas as crianças. - **leis contra trabalho infantil**: tira das crianças a oportunidade de aprender ofícios úteis e levar um dinheiro para ajudar a família. - **licitações**: como não existem os critérios do mercado para decidir qual é o melhor prestador de serviço, criam-se comissões de pessoas que vão decidir coisas. isto incentiva os prestadores de serviço que estão concorrendo na licitação a tentar comprar os membros dessas comissões. isto, fora a corrupção, gera problemas reais: __(i)__ a escolha dos serviços acaba sendo a pior possível, já que a empresa prestadora que vence está claramente mais dedicada a comprar comissões do que a fazer um bom trabalho (este problema afeta tantas áreas, desde a construção de estradas até a qualidade da merenda escolar, que é impossível listar aqui); __(ii)__ o processo corruptor acaba, no longo prazo, eliminando as empresas que prestavam e deixando para competir apenas as corruptas, e a qualidade tende a piorar progressivamente. - **cartéis**: o Estado em geral cria e depois fica refém de vários grupos de interesse. o caso dos taxistas contra o Uber é o que está na moda hoje (e o que mostra como os Estados se comportam da mesma forma no mundo todo). - **multas**: quando algum indivíduo ou empresa comete uma fraude financeira, ou causa algum dano material involuntário, as vítimas do caso são as pessoas que sofreram o dano ou perderam dinheiro, mas o Estado tem sempre leis que prevêem multas para os responsáveis. A justiça estatal é sempre muito rígida e rápida na aplicação dessas multas, mas relapsa e vaga no que diz respeito à indenização das vítimas. O que em geral acontece é que o Estado aplica uma enorme multa ao responsável pelo mal, retirando deste os recursos que dispunha para indenizar as vítimas, e se retira do caso, deixando estas desamparadas. - **desapropriação**: o Estado pode pegar qualquer propriedade de qualquer pessoa mediante uma indenização que é necessariamente inferior ao valor da propriedade para o seu presente dono (caso contrário ele a teria vendido voluntariamente). - **seguro-desemprego**: se há, por exemplo, um prazo mínimo de 1 ano para o sujeito ter direito a receber seguro-desemprego, isto o incentiva a planejar ficar apenas 1 ano em cada emprego (ano este que será sucedido por um período de desemprego remunerado), matando todas as possibilidades de aprendizado ou aquisição de experiência naquela empresa específica ou ascensão hierárquica. - **previdência**: a previdência social tem todos os defeitos de cálculo do mundo, e não importa muito ela ser uma forma horrível de poupar dinheiro, porque ela tem garantias bizarras de longevidade fornecidas pelo Estado, além de ser compulsória. Isso serve para criar no imaginário geral a idéia da __aposentadoria__, uma época mágica em que todos os dias serão finais de semana. A idéia da aposentadoria influencia o sujeito a não se preocupar em ter um emprego que faça sentido, mas sim em ter um trabalho qualquer, que o permita se aposentar. - **regulamentação impossível**: milhares de coisas são proibidas, há regulamentações sobre os aspectos mais mínimos de cada empreendimento ou construção ou espaço. se todas essas regulamentações fossem exigidas não haveria condições de produção e todos morreriam. portanto, elas não são exigidas. porém, o Estado, ou um agente individual imbuído do poder estatal pode, se desejar, exigi-las todas de um cidadão inimigo seu. qualquer pessoa pode viver a vida inteira sem cumprir nem 10% das regulamentações estatais, mas viverá também todo esse tempo com medo de se tornar um alvo de sua exigência, num estado de terror psicológico. - **perversão de critérios**: para muitas coisas sobre as quais a sociedade normalmente chegaria a um valor ou comportamento "razoável" espontaneamente, o Estado dita regras. estas regras muitas vezes não são obrigatórias, são mais "sugestões" ou limites, como o salário mínimo, ou as 44 horas semanais de trabalho. a sociedade, porém, passa a usar esses valores como se fossem o normal. são raras, por exemplo, as ofertas de emprego que fogem à regra das 44h semanais. - **inflação**: subir os preços é difícil e constrangedor para as empresas, pedir aumento de salário é difícil e constrangedor para o funcionário. a inflação força as pessoas a fazer isso, mas o aumento não é automático, como alguns economistas podem pensar (enquanto alguns outros ficam muito satisfeitos de que esse processo seja demorado e difícil). - **inflação**: a inflação destrói a capacidade das pessoas de julgar preços entre concorrentes usando a própria memória. - **inflação**: a inflação destrói os cálculos de lucro/prejuízo das empresas e prejudica enormemente as decisões empresariais que seriam baseadas neles. - **inflação**: a inflação redistribui a riqueza dos mais pobres e mais afastados do sistema financeiro para os mais ricos, os bancos e as megaempresas. - **inflação**: a inflação estimula o endividamento e o consumismo. - **lixo:** ao prover coleta e armazenamento de lixo "grátis para todos" o Estado incentiva a criação de lixo. se tivessem que pagar para que recolhessem o seu lixo, as pessoas (e conseqüentemente as empresas) se empenhariam mais em produzir coisas usando menos plástico, menos embalagens, menos sacolas. - **leis contra crimes financeiros:** ao criar legislação para dificultar acesso ao sistema financeiro por parte de criminosos a dificuldade e os custos para acesso a esse mesmo sistema pelas pessoas de bem cresce absurdamente, levando a um percentual enorme de gente incapaz de usá-lo, para detrimento de todos -- e no final das contas os grandes criminosos ainda conseguem burlar tudo. -
 @ 3bf0c63f:aefa459d
2025-04-25 18:55:52
@ 3bf0c63f:aefa459d
2025-04-25 18:55:52Report of how the money Jack donated to the cause in December 2022 has been misused so far.
Bounties given
March 2025
- Dhalsim: 1,110,540 - Work on Nostr wiki data processing
February 2025
- BOUNTY* NullKotlinDev: 950,480 - Twine RSS reader Nostr integration
- Dhalsim: 2,094,584 - Work on Hypothes.is Nostr fork
- Constant, Biz and J: 11,700,588 - Nostr Special Forces
January 2025
- Constant, Biz and J: 11,610,987 - Nostr Special Forces
- BOUNTY* NullKotlinDev: 843,840 - Feeder RSS reader Nostr integration
- BOUNTY* NullKotlinDev: 797,500 - ReadYou RSS reader Nostr integration
December 2024
- BOUNTY* tijl: 1,679,500 - Nostr integration into RSS readers yarr and miniflux
- Constant, Biz and J: 10,736,166 - Nostr Special Forces
- Thereza: 1,020,000 - Podcast outreach initiative
November 2024
- Constant, Biz and J: 5,422,464 - Nostr Special Forces
October 2024
- Nostrdam: 300,000 - hackathon prize
- Svetski: 5,000,000 - Latin America Nostr events contribution
- Quentin: 5,000,000 - nostrcheck.me
June 2024
- Darashi: 5,000,000 - maintaining nos.today, searchnos, search.nos.today and other experiments
- Toshiya: 5,000,000 - keeping the NIPs repo clean and other stuff
May 2024
- James: 3,500,000 - https://github.com/jamesmagoo/nostr-writer
- Yakihonne: 5,000,000 - spreading the word in Asia
- Dashu: 9,000,000 - https://github.com/haorendashu/nostrmo
February 2024
- Viktor: 5,000,000 - https://github.com/viktorvsk/saltivka and https://github.com/viktorvsk/knowstr
- Eric T: 5,000,000 - https://github.com/tcheeric/nostr-java
- Semisol: 5,000,000 - https://relay.noswhere.com/ and https://hist.nostr.land relays
- Sebastian: 5,000,000 - Drupal stuff and nostr-php work
- tijl: 5,000,000 - Cloudron, Yunohost and Fraidycat attempts
- Null Kotlin Dev: 5,000,000 - AntennaPod attempt
December 2023
- hzrd: 5,000,000 - Nostrudel
- awayuki: 5,000,000 - NOSTOPUS illustrations
- bera: 5,000,000 - getwired.app
- Chris: 5,000,000 - resolvr.io
- NoGood: 10,000,000 - nostrexplained.com stories
October 2023
- SnowCait: 5,000,000 - https://nostter.vercel.app/ and other tools
- Shaun: 10,000,000 - https://yakihonne.com/, events and work on Nostr awareness
- Derek Ross: 10,000,000 - spreading the word around the world
- fmar: 5,000,000 - https://github.com/frnandu/yana
- The Nostr Report: 2,500,000 - curating stuff
- james magoo: 2,500,000 - the Obsidian plugin: https://github.com/jamesmagoo/nostr-writer
August 2023
- Paul Miller: 5,000,000 - JS libraries and cryptography-related work
- BOUNTY tijl: 5,000,000 - https://github.com/github-tijlxyz/wikinostr
- gzuus: 5,000,000 - https://nostree.me/
July 2023
- syusui-s: 5,000,000 - rabbit, a tweetdeck-like Nostr client: https://syusui-s.github.io/rabbit/
- kojira: 5,000,000 - Nostr fanzine, Nostr discussion groups in Japan, hardware experiments
- darashi: 5,000,000 - https://github.com/darashi/nos.today, https://github.com/darashi/searchnos, https://github.com/darashi/murasaki
- jeff g: 5,000,000 - https://nostr.how and https://listr.lol, plus other contributions
- cloud fodder: 5,000,000 - https://nostr1.com (open-source)
- utxo.one: 5,000,000 - https://relaying.io (open-source)
- Max DeMarco: 10,269,507 - https://www.youtube.com/watch?v=aA-jiiepOrE
- BOUNTY optout21: 1,000,000 - https://github.com/optout21/nip41-proto0 (proposed nip41 CLI)
- BOUNTY Leo: 1,000,000 - https://github.com/leo-lox/camelus (an old relay thing I forgot exactly)
June 2023
- BOUNTY: Sepher: 2,000,000 - a webapp for making lists of anything: https://pinstr.app/
- BOUNTY: Kieran: 10,000,000 - implement gossip algorithm on Snort, implement all the other nice things: manual relay selection, following hints etc.
- Mattn: 5,000,000 - a myriad of projects and contributions to Nostr projects: https://github.com/search?q=owner%3Amattn+nostr&type=code
- BOUNTY: lynn: 2,000,000 - a simple and clean git nostr CLI written in Go, compatible with William's original git-nostr-tools; and implement threaded comments on https://github.com/fiatjaf/nocomment.
- Jack Chakany: 5,000,000 - https://github.com/jacany/nblog
- BOUNTY: Dan: 2,000,000 - https://metadata.nostr.com/
April 2023
- BOUNTY: Blake Jakopovic: 590,000 - event deleter tool, NIP dependency organization
- BOUNTY: koalasat: 1,000,000 - display relays
- BOUNTY: Mike Dilger: 4,000,000 - display relays, follow event hints (Gossip)
- BOUNTY: kaiwolfram: 5,000,000 - display relays, follow event hints, choose relays to publish (Nozzle)
- Daniele Tonon: 3,000,000 - Gossip
- bu5hm4nn: 3,000,000 - Gossip
- BOUNTY: hodlbod: 4,000,000 - display relays, follow event hints
March 2023
- Doug Hoyte: 5,000,000 sats - https://github.com/hoytech/strfry
- Alex Gleason: 5,000,000 sats - https://gitlab.com/soapbox-pub/mostr
- verbiricha: 5,000,000 sats - https://badges.page/, https://habla.news/
- talvasconcelos: 5,000,000 sats - https://migrate.nostr.com, https://read.nostr.com, https://write.nostr.com/
- BOUNTY: Gossip model: 5,000,000 - https://camelus.app/
- BOUNTY: Gossip model: 5,000,000 - https://github.com/kaiwolfram/Nozzle
- BOUNTY: Bounty Manager: 5,000,000 - https://nostrbounties.com/
February 2023
- styppo: 5,000,000 sats - https://hamstr.to/
- sandwich: 5,000,000 sats - https://nostr.watch/
- BOUNTY: Relay-centric client designs: 5,000,000 sats https://bountsr.org/design/2023/01/26/relay-based-design.html
- BOUNTY: Gossip model on https://coracle.social/: 5,000,000 sats
- Nostrovia Podcast: 3,000,000 sats - https://nostrovia.org/
- BOUNTY: Nostr-Desk / Monstr: 5,000,000 sats - https://github.com/alemmens/monstr
- Mike Dilger: 5,000,000 sats - https://github.com/mikedilger/gossip
January 2023
- ismyhc: 5,000,000 sats - https://github.com/Galaxoid-Labs/Seer
- Martti Malmi: 5,000,000 sats - https://iris.to/
- Carlos Autonomous: 5,000,000 sats - https://github.com/BrightonBTC/bija
- Koala Sat: 5,000,000 - https://github.com/KoalaSat/nostros
- Vitor Pamplona: 5,000,000 - https://github.com/vitorpamplona/amethyst
- Cameri: 5,000,000 - https://github.com/Cameri/nostream
December 2022
- William Casarin: 7 BTC - splitting the fund
- pseudozach: 5,000,000 sats - https://nostr.directory/
- Sondre Bjellas: 5,000,000 sats - https://notes.blockcore.net/
- Null Dev: 5,000,000 sats - https://github.com/KotlinGeekDev/Nosky
- Blake Jakopovic: 5,000,000 sats - https://github.com/blakejakopovic/nostcat, https://github.com/blakejakopovic/nostreq and https://github.com/blakejakopovic/NostrEventPlayground
-
 @ 3bf0c63f:aefa459d
2024-01-14 14:52:16
@ 3bf0c63f:aefa459d
2024-01-14 14:52:16bitcoinddecentralizationIt is better to have multiple curator teams, with different vetting processes and release schedules for
bitcoindthan a single one."More eyes on code", "Contribute to Core", "Everybody should audit the code".
All these points repeated again and again fell to Earth on the day it was discovered that Bitcoin Core developers merged a variable name change from "blacklist" to "blocklist" without even discussing or acknowledging the fact that that innocent pull request opened by a sybil account was a social attack.
After a big lot of people manifested their dissatisfaction with that event on Twitter and on GitHub, most Core developers simply ignored everybody's concerns or even personally attacked people who were complaining.
The event has shown that:
1) Bitcoin Core ultimately rests on the hands of a couple maintainers and they decide what goes on the GitHub repository[^pr-merged-very-quickly] and the binary releases that will be downloaded by thousands; 2) Bitcoin Core is susceptible to social attacks; 2) "More eyes on code" don't matter, as these extra eyes can be ignored and dismissed.
Solution:
bitcoinddecentralizationIf usage was spread across 10 different
bitcoindflavors, the network would be much more resistant to social attacks to a single team.This has nothing to do with the question on if it is better to have multiple different Bitcoin node implementations or not, because here we're basically talking about the same software.
Multiple teams, each with their own release process, their own logo, some subtle changes, or perhaps no changes at all, just a different name for their
bitcoindflavor, and that's it.Every day or week or month or year, each flavor merges all changes from Bitcoin Core on their own fork. If there's anything suspicious or too leftist (or perhaps too rightist, in case there's a leftist
bitcoindflavor), maybe they will spot it and not merge.This way we keep the best of both worlds: all software development, bugfixes, improvements goes on Bitcoin Core, other flavors just copy. If there's some non-consensus change whose efficacy is debatable, one of the flavors will merge on their fork and test, and later others -- including Core -- can copy that too. Plus, we get resistant to attacks: in case there is an attack on Bitcoin Core, only 10% of the network would be compromised. the other flavors would be safe.
Run Bitcoin Knots
The first example of a
bitcoindsoftware that follows Bitcoin Core closely, adds some small changes, but has an independent vetting and release process is Bitcoin Knots, maintained by the incorruptible Luke DashJr.Next time you decide to run
bitcoind, run Bitcoin Knots instead and contribute tobitcoinddecentralization!
See also:
[^pr-merged-very-quickly]: See PR 20624, for example, a very complicated change that could be introducing bugs or be a deliberate attack, merged in 3 days without time for discussion.
-
 @ 8bf578f4:b6303c41
2025-05-23 12:09:02
@ 8bf578f4:b6303c41
2025-05-23 12:09:02test2
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ 502ab02a:a2860397
2025-05-24 01:14:43
@ 502ab02a:a2860397
2025-05-24 01:14:43ในสายตาคนรักสุขภาพทั่วโลก “อโวคาโด” คือผลไม้ในฝัน มันมีไขมันดี มีไฟเบอร์สูง ช่วยลดคอเลสเตอรอลได้ มีวิตามินอี มีโพแทสเซียม และที่สำคัญคือ "ดูดี" ทุกครั้งที่ถูกปาดวางบนขนมปังโฮลวีตในชามสลัด หรือบนโฆษณาอาหารคลีนสุดหรู
แต่ในสายตาชาวไร่บางคนในเม็กซิโกหรือชุมชนพื้นเมืองในโดมินิกัน อโวคาโดไม่ใช่ผลไม้แห่งสุขภาพ แต่มันคือสัญลักษณ์ของความรุนแรง การกดขี่ และการสูญเสียเสรีภาพในผืนดินของตัวเอง
เมื่ออาหารกลายเป็นทองคำ กลุ่มอิทธิพลก็ไม่เคยพลาดจะเข้าครอบครอง
เรามักได้ยินคำว่า "ทองคำเขียว" หรือ Green Gold ใช้เรียกอโวคาโด เพราะในรอบ 20 ปีที่ผ่านมา ความต้องการบริโภคของมันพุ่งสูงขึ้นเป็นเท่าตัว โดยเฉพาะในสหรัฐฯ และยุโรป จากผลการวิจัยของมหาวิทยาลัยฮาร์วาร์ดและข้อมูลการส่งออกของ USDA พบว่า 90% ของอโวคาโดที่บริโภคในอเมริกา มาจากรัฐมิโชอากังของเม็กซิโก พื้นที่ซึ่งควบคุมโดยกลุ่มค้ายาเสพติดไม่ต่างจากเจ้าของสวนตัวจริง
พวกเขาเรียกเก็บ “ค่าคุ้มครอง” จากเกษตรกร โดยใช้วิธีเดียวกับมาเฟีย คือ ถ้าไม่จ่าย ก็เจ็บตัวหรือหายตัว ไม่ว่าจะเป็นกลุ่ม CJNG (Jalisco New Generation Cartel), Familia Michoacana หรือ Caballeros Templarios พวกเขาไม่ได้สนใจว่าใครปลูกหรือใครรดน้ำ ตราบใดที่ผลผลิตสามารถเปลี่ยนเป็นเงินได้
องค์กรอาชญากรรมเหล่านี้ไม่ได้แค่ “แฝงตัว” ในอุตสาหกรรม แต่ ยึดครอง ห่วงโซ่การผลิตทั้งหมด ตั้งแต่แปลงปลูกไปจนถึงโรงบรรจุและเส้นทางขนส่ง คนที่ไม่ยอมเข้าระบบมืดอาจต้องพบจุดจบในป่า หรือไม่มีชื่ออยู่ในทะเบียนบ้านอีกต่อไป
จากรายงานของเว็บไซต์ Food is Power องค์กรไม่แสวงกำไรด้านความยุติธรรมด้านอาหารในสหรัฐฯ เผยว่า ในปี 2020 มีเกษตรกรในเม็กซิโกจำนวนมากที่ถูกข่มขู่ บางรายถึงขั้นถูกฆาตกรรม เพราะปฏิเสธจ่ายค่าคุ้มครองจากกลุ่มค้ายา
การปลูกอโวคาโดไม่ใช่เรื่องเบาๆ กับธรรมชาติ เพราะมันต้องการ “น้ำ” มากถึง 272 ลิตรต่อผลเดียว! เรามาดูว่า “272 ลิตร” นี้ เท่ากับอะไรบ้างในชีวิตจริง อาบน้ำฝักบัวนาน 10–12 นาที (โดยเฉลี่ยใช้น้ำ 20–25 ลิตรต่อนาที) ใช้น้ำซักเสื้อผ้าเครื่องหนึ่ง (เครื่องซักผ้า 1 ครั้งกินประมาณ 60–100 ลิตร) น้ำดื่มของคนหนึ่งคนได้นานเกือบ เดือน (คนเราต้องการน้ำดื่มประมาณ 1.5–2 ลิตรต่อวัน)
ถ้าเราใช้ข้อมูลจาก FAO และ Water Footprint Network การผลิตเนื้อวัว 1 กิโลกรัม ต้องใช้น้ำ 15,000 ลิตร (รวมทั้งการปลูกหญ้า อาหารสัตว์ การดื่มน้ำของวัว ฯลฯ) ได้โปรตีนราว 250 กรัม อโวคาโด 1 กิโลกรัม (ราว 5 ผล) ใช้น้ำประมาณ 1,360 ลิตร ได้โปรตีนเพียง 6–8 กรัมเท่านั้น พูดง่ายๆคือ เมื่อเทียบอัตราส่วนเป็นลิตรต่อกรัมโปรตีนแล้วนั้น วัวใช้น้ำ 60 ลิตรต่อกรัมโปรตีน / อโวคาโด ใช้น้ำ 194 ลิตรต่อกรัมโปรตีน แถมการเลี้ยงวัวในระบบธรรมชาติ (เช่น pasture-raised หรือ regenerative farming) ยังสามารถเป็นส่วนหนึ่งของระบบหมุนเวียนน้ำและคาร์บอนได้ พอเห็นภาพแล้วใช่ไหมครับ ดังนั้นเราควรระมัดระวังการเสพสื่อเอาไว้ด้วยว่า คำว่า "ดีต่อโลก" ไม่ได้หมายถึงพืชอย่างเดียว ทุกธุรกิจถ้าทำแบบที่ควรทำ มันยังสามารถผลักดันโลกไม่ให้ตกอยู่ในมือองค์กร future food ได้ เพราะมูลค่ามันสูงมาก
และเมื่อราคาสูง พื้นที่เพาะปลูกก็ขยายอย่างไร้การควบคุม ป่าธรรมชาติในรัฐมิโชอากังถูกแอบโค่นแบบผิดกฎหมายเพื่อแปลงสภาพเป็นไร่ “ทองเขียว” ข้อมูลจาก Reuters พบว่าผลไม้ที่ถูกส่งออกไปยังสหรัฐฯ บางส่วนมาจากแปลงปลูกที่บุกรุกป่าคุ้มครอง และรัฐบาลเองก็ไม่สามารถควบคุมได้เพราะอิทธิพลของกลุ่มทุนและมาเฟีย
ในโดมินิกันก็เช่นกัน มีรายงานจากสำนักข่าว Gestalten ว่าพื้นที่ป่าสงวนหลายพันไร่ถูกเปลี่ยนเป็นไร่อโวคาโด เพื่อป้อนตลาดผู้บริโภคในอเมริกาและยุโรปโดยตรง โดยไม่มีการชดเชยใดๆ แก่ชุมชนท้องถิ่น
สุขภาพที่ดีไม่ควรได้มาจากการทำลายสุขภาพของคนอื่น ไม่ควรมีผลไม้ใดที่ดูดีในจานของเรา แล้วเบื้องหลังเต็มไปด้วยคราบเลือดและน้ำตาของคนปลูก
เฮียไม่ได้จะบอกให้เลิกกินอโวคาโดเลย แต่เฮียอยากให้เรารู้ทัน ว่าความนิยมของอาหารสุขภาพวันนี้ กำลังเป็นสนามใหม่ของกลุ่มทุนโลก ที่พร้อมจะครอบครองด้วย “อำนาจอ่อน” ผ่านแบรนด์อาหารธรรมชาติ ผ่านกฎหมายสิ่งแวดล้อม หรือแม้แต่การครอบงำตลาดเสรีด้วยกำลังอาวุธ
นี่ไม่ใช่เรื่องไกลตัว เพราะเมื่อกลุ่มทุนเริ่มฮุบเมล็ดพันธุ์ คุมเส้นทางขนส่ง คุมฉลาก Certified Organic ทั้งหลาย พวกเขาก็ “ควบคุมสุขภาพ” ของผู้บริโภคเมืองอย่างเราไปด้วยโดยอ้อม
คำถามสำคัญที่มาทุกครั้งเวลามีเนื้อหาอะไรมาฝากคือ แล้วเราจะทำอะไรได้? 555555 - เลือกบริโภคผลไม้จากแหล่งที่โปร่งใสหรือปลูกเองได้ - สนับสนุนเกษตรกรรายย่อยที่ไม่อยู่ภายใต้กลุ่มทุน - ใช้เสียงของผู้บริโภคกดดันให้มีระบบตรวจสอบต้นทางจริง ไม่ใช่แค่ฉลากเขียวสวยๆ - และที่สำคัญ อย่าเชื่อว่า “ทุกสิ่งที่เขาวางให้ดูสุขภาพดี” จะดีจริง (ข้อนี่ละตัวดีเลยครับ)
สุขภาพไม่ใช่สินค้า และอาหารไม่ควรเป็นอาวุธของกลุ่มทุน หากเราเริ่มตระหนักว่าอาหารคือการเมือง น้ำคืออำนาจ และแปลงเกษตรคือสนามรบ เฮียเชื่อว่าผู้บริโภคอย่างเราจะไม่ยอมเป็นหมากอีกต่อไป #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 3f770d65:7a745b24
2024-12-30 19:25:45
@ 3f770d65:7a745b24
2024-12-30 19:25:45As I look back on my predictions for Nostr in 2024, it’s clear I had some hits and misses. I believe my first two predictions were spot on, accurately reflecting the trends and developments we witnessed. However, my second two predictions missed the mark, proving to be far less accurate. Maybe I was too bullish?
nostr:nevent1qvzqqqqqqypzq0mhp4ja8fmy48zuk5p6uy37vtk8tx9dqdwcxm32sy8nsaa8gkeyqyghwumn8ghj7mn0wd68ytnhd9hx2tcpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtcqypsm9tk39g20atwqskvjcvhq7rher5nkgwjr05lzspne4gf0uvyxukew5mg
What did I get right? Clients did increasingly prioritize user and content discovery while enabling users to easily select and choose their own algorithms. (DVMs, Trending, What's Hot, Feeds, etc.) This focus provided individuals with more tools, greater control, and unprecedented power over their social streams and attention than ever before. This is still actively happening and will continue to happen throughout 2025 too.
What did I get wrong? We didn't see an Other Stuff application breakthrough as a clear winner that became a mainstream favorite. I anticipated a standout application that would interest users and become a "must-use" within the ecosystem, but this didn’t happen. And we also clearly didn't hit 1M active users either. While adoption did increase, it didn’t reach the critical mass I expected.
But this doesn't mean 2024 fell short of expectations—in fact, quite the opposite. The year brought incredible client innovations (Damus Notedeck, Primal 2.0, TOR only Amethyst, Flotilla, Chachi, Olas, Coracle feeds, etc.) and relay milestones (Web-of-Trust relays, private relays, algorithm based relays, etc.) with the introduction of these innovative features and the launch of these new platforms.
Beyond technology, the Nostr community achieved something truly remarkable: a grassroots movement that united people globally.
From supporting Nostr meetups and events to hosting booths across continents at major conferences, the community came together to raise money to support these initiatives in ways no one predicted. This organic, ground-up effort showcased the strength and passion behind Nostr, creating a foundation that will #grownostr and success for years to come.
Too bullish? Maybe I wasn't bullish enough? As is tradition, I will post my 2025 predictions tomorrow.
-
 @ 8bf578f4:b6303c41
2025-05-23 12:06:59
@ 8bf578f4:b6303c41
2025-05-23 12:06:59test 1234
hello
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 05a0f81e:fc032124
2025-05-23 19:50:46
@ 05a0f81e:fc032124
2025-05-23 19:50:46I was discussing with my friend and few of his friends about the inflation of naira in Nigeria 🇳🇬. Our discussions was flowing until he said that lack of production and too much importations are the major reason that devalued currencies, naira to be precise. As a baby bitcioner, I disagree with him and that's where our discussion turn to argument.
People often think that when a country prioritize productions than consumption that it will boost the value of there currency, but that is wrong. Production have it's impart on the economy of the country.
Increased Economic Growth: A trade surplus indicates that a country's output is high, contributing to overall economic growth, as measured by GDP.
Stimulated Consumer Spending: The influx of foreign currency from exports can be used to import goods, stimulating domestic demand and boosting consumer spending.
Potential for Higher Wages and Living Standards: Increased productivity and economic growth can lead to higher wages and a better standard of living.
Savings and Investment: The surplus can be used for savings, investment in infrastructure, or to reduce debt, further strengthening the economy.
Comparative Advantage: A country may specialize in producing goods and services where it has a comparative advantage, leading to higher productivity and efficiency.
Moreover, too production and exportation also causes inflation. country exports too much and its domestic demand doesn't keep pace, it could lead to inflation as businesses raise prices to cover increased production cost.
Meanwhile, the head lead of currency inflation is the printing of money in the air!.
"Printing money in the air" likely refers to the concept of central banks creating new money digitally, often through quantitative easing. This process involves the central bank buying assets, such as government bonds, from banks and other financial institutions, thereby injecting new money into the economy.
How it Works:
-
Digital Money Creation: The central bank creates new money electronically, rather than physically printing currency notes.
-
Asset Purchases: The central bank buys assets from banks and other financial institutions, injecting new money into the economy.
-
Increased Money Supply: This process expands the money supply, which can lead to lower interest rates and increased lending.
Key Points:
-
Quantitative Easing (QE): A monetary policy tool used by central banks to stimulate economic growth by buying assets and injecting new money into the economy.
-
No Physical Printing: Unlike traditional money printing, QE creates digital money, which is then used to purchase assets.
-
Impact on Economy: QE can influence interest rates, inflation, and economic growth.
The role of Central Bank's.
The central bank plays a crucial role in managing the money supply and implementing monetary policies, including QE. By controlling interest rates and the money supply, central banks aim to promote economic growth, stability, and low inflation.
There are key 🔑 negative effects of printing currency notes on air!:
Printing money, also known as quantitative easing, can have several negative effects on the economy. Some of the key concerns include;
-
Inflation: Excessive money printing can lead to inflation, as more money chases a constant amount of goods and services, driving up prices. This can erode the purchasing power of consumers and reduce the value of savings.
-
Currency Devaluation: Printing money can cause a decline in the value of a currency, making imports more expensive and potentially leading to higher prices for consumers.
-
Distorted Financial Markets: The injection of liquidity into the economy can artificially inflate asset prices, creating market distortions and potentially leading to asset bubbles.
-
Uncertainty and Confusion: High inflation can create uncertainty and confusion for businesses and individuals, making it harder to make informed investment decisions.
-
Reduced Incentive to Save: Inflation can reduce the incentive to save, as the value of money declines over time.
-
Menu Costs: High inflation can lead to menu costs, where businesses incur expenses to update prices frequently.
-
Inefficient Allocation of Resources: Government spending funded by printing money can lead to inefficient allocation of resources, as decisions are driven by politics rather than market forces.
-
Addiction to Fiscal Stimulus: The ease of printing money can create a dependency on fiscal stimulus, making it challenging to reverse course when economic conditions change.
-
Long-term Consequences: The long-term consequences of printing money can be severe, including reduced economic growth, higher inflation, and decreased confidence in the currency.
It's worth noting that the impact of printing money can vary depending on the economic context. In times of recession or deflation, moderate money printing might be used to stimulate economic growth without triggering significant inflation. However, excessive or prolonged money printing can lead to negative consequences.
-
-
 @ 4ba8e86d:89d32de4
2025-05-19 10:13:19
@ 4ba8e86d:89d32de4
2025-05-19 10:13:19DTails é uma ferramenta que facilita a inclusão de aplicativos em imagens de sistemas live baseados em Debian, como o Tails. Com ela, você pode personalizar sua imagem adicionando os softwares que realmente precisa — tudo de forma simples, transparente e sob seu controle total.
⚠️ DTails não é uma distribuição. É uma ferramenta de remasterização de imagens live.
Ela permite incluir softwares como:
✅ SimpleX Chat ✅ Clientes Nostr Web (Snort & Iris) ✅ Sparrow Wallet ✅ Feather Wallet ✅ Cake Wallet ✅ RoboSats ✅ Bisq ✅ BIP39 (Ian Coleman) ✅ SeedTool ... e muito mais. https://image.nostr.build/b0bb1f0da5a9a8fee42eacbddb156fc3558f4c3804575d55eeefbe6870ac223e.jpg
Importante: os binários originais dos aplicativos não são modificados, garantindo total transparência e permitindo a verificação de hashes a qualquer momento.
👨💻 Desenvolvido por: nostr:npub1dtmp3wrkyqafghjgwyk88mxvulfncc9lg6ppv4laet5cun66jtwqqpgte6
GitHub: https://github.com/DesobedienteTecnologico/dtails?tab=readme-ov-file
🎯 Controle total do que será instalado
Com o DTails, você escolhe exatamente o que deseja incluir na imagem personalizada. Se não marcar um aplicativo, ele não será adicionado, mesmo que esteja disponível. Isso significa: privacidade, leveza e controle absoluto.
https://image.nostr.build/b0bb1f0da5a9a8fee42eacbddb156fc3558f4c3804575d55eeefbe6870ac223e.jpg https://image.nostr.build/b70ed11ad2ce0f14fd01d62c08998dc18e3f27733c8d7e968f3459846fb81baf.jpg https://image.nostr.build/4f5a904218c1ea6538be5b3f764eefda95edd8f88b2f42ac46b9ae420b35e6f6.jpg
⚙️ Começando com o DTails
📦 Requisitos de pacotes
Antes de tudo, instale os seguintes pacotes no Debian:
``` sudo apt-get install genisoimage parted squashfs-tools syslinux-utils build-essential python3-tk python3-pil.imagetk python3-pyudev
```
🛠 Passo a passo
1 Clone o repositório:
``` git clone https://github.com/DesobedienteTecnologico/dtails cd dtails
```
2 Inicie a interface gráfica com sudo:
``` sudo ./dtails.py
```
Por que usar sudo? É necessário para montar arquivos .iso ou .img e utilizar ferramentas essenciais do sistema.
💿 Selecione a imagem Tails que deseja modificar
https://nostr.download/e3143dcd72ab6dcc86228be04d53131ccf33d599a5f7f2f1a5c0d193557dac6b.jpg
📥 Adicione ou remova pacotes
1 Marque os aplicativos desejados. 2 Clique Buildld para gerar sua imagem personalizada. https://image.nostr.build/5c4db03fe33cd53d06845074d03888a3ca89c3e29b2dc1afed4d9d181489b771.png
Você pode acompanhar todo o processo diretamente no terminal. https://nostr.download/1d959f4be4de9fbb666ada870afee4a922fb5e96ef296c4408058ec33cd657a8.jpg
💽 .ISO vs .IMG — Qual escolher?
| Formato | Persistência | Observações | | ------- | ---------------------- | ----------------------------------------------- | | .iso | ❌ Não tem persistência | Gera o arquivo DTails.iso na pasta do projeto | | .img | ✅ Suporta persistência | Permite gravar diretamente em um pendrive |
https://nostr.download/587fa3956df47a38b169619f63c559928e6410c3dd0d99361770a8716b3691f6.jpg https://nostr.download/40c7c5badba765968a1004ebc67c63a28b9ae3b5801addb02166b071f970659f.jpg
vídeo
https://www.youtube.com/live/QABz-GOeQ68?si=eYX-AHsolbp_OmAm
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 5c26ee8b:a4d229aa
2025-05-23 08:47:45
@ 5c26ee8b:a4d229aa
2025-05-23 08:47:45Generally mentioning God, Allah, by reciting/reading the Quran or performing Salat (compulsory prayer), for instance, brings tranquility to the heart of the believer. The Salat, other than being the first deed a Muslim would be questioned about on Judgement Day, it keeps the person away from the forbidden wrong deeds too. The Salat is sufficient for obtaining God’s provision as he decrees the means for it to reach the person. Wasting or missing performing the Salat or mentioning God (Allah) by reciting/reading the Quran or Tasbieh, can lead to following the desires only and a depressed life as well as punishment in the Thereafter.
13:28 Ar-Ra'd
الَّذِينَ آمَنُوا وَتَطْمَئِنُّ قُلُوبُهُمْ بِذِكْرِ اللَّهِ ۗ أَلَا بِذِكْرِ اللَّهِ تَطْمَئِنُّ الْقُلُوبُ
Those who have believed and whose hearts are assured (tranquillised) by the remembrance of Allah. Unquestionably, by the remembrance of Allah hearts are assured (tranquillised)."
29:45 Al-Ankaboot
اتْلُ مَا أُوحِيَ إِلَيْكَ مِنَ الْكِتَابِ وَأَقِمِ الصَّلَاةَ ۖ إِنَّ الصَّلَاةَ تَنْهَىٰ عَنِ الْفَحْشَاءِ وَالْمُنْكَرِ ۗ وَلَذِكْرُ اللَّهِ أَكْبَرُ ۗ وَاللَّهُ يَعْلَمُ مَا تَصْنَعُونَ
Recite, [O Muhammad], what has been revealed to you of the Book and establish prayer. Indeed, prayer prohibits immorality and wrongdoing, and the remembrance of Allah is greater. And Allah knows that which you do.
11:114 Hud
وَأَقِمِ الصَّلَاةَ طَرَفَيِ النَّهَارِ وَزُلَفًا مِنَ اللَّيْلِ ۚ إِنَّ الْحَسَنَاتِ يُذْهِبْنَ السَّيِّئَاتِ ۚ ذَٰلِكَ ذِكْرَىٰ لِلذَّاكِرِينَ
And establish prayer at the two ends of the day and at the approach of the night. Indeed, good deeds do away with misdeeds. That is a reminder for those who remember.
20:132 Taa-Haa
وَأْمُرْ أَهْلَكَ بِالصَّلَاةِ وَاصْطَبِرْ عَلَيْهَا ۖ لَا نَسْأَلُكَ رِزْقًا ۖ نَحْنُ نَرْزُقُكَ ۗ وَالْعَاقِبَةُ لِلتَّقْوَىٰ
And enjoin prayer upon your family [and people] and be steadfast therein. We ask you not for provision; We provide for you, and the [best] outcome is for [those of] righteousness.
20:124 Taa-Haa
وَمَنْ أَعْرَضَ عَنْ ذِكْرِي فَإِنَّ لَهُ مَعِيشَةً ضَنْكًا وَنَحْشُرُهُ يَوْمَ الْقِيَامَةِ أَعْمَىٰ
And whoever turns away from My remembrance - indeed, he will have a depressed life, and We will gather him on the Day of Resurrection blind."
20:125 Taa-Haa
قَالَ رَبِّ لِمَ حَشَرْتَنِي أَعْمَىٰ وَقَدْ كُنْتُ بَصِيرًا
He will say, "My Lord, why have you raised me blind while I was [once] seeing?"
20:126 Taa-Haa
قَالَ كَذَٰلِكَ أَتَتْكَ آيَاتُنَا فَنَسِيتَهَا ۖ وَكَذَٰلِكَ الْيَوْمَ تُنْسَىٰ
[Allah] will say, "Thus did Our signs come to you, and you forgot them; and thus will you this Day be forgotten."
20:127 Taa-Haa
وَكَذَٰلِكَ نَجْزِي مَنْ أَسْرَفَ وَلَمْ يُؤْمِنْ بِآيَاتِ رَبِّهِ ۚ وَلَعَذَابُ الْآخِرَةِ أَشَدُّ وَأَبْقَىٰ
And thus do We recompense he who transgressed and did not believe in the signs of his Lord. And the punishment of the Hereafter is more severe and more enduring.
20:128 Taa-Haa
أَفَلَمْ يَهْدِ لَهُمْ كَمْ أَهْلَكْنَا قَبْلَهُمْ مِنَ الْقُرُونِ يَمْشُونَ فِي مَسَاكِنِهِمْ ۗ إِنَّ فِي ذَٰلِكَ لَآيَاتٍ لِأُولِي النُّهَىٰ
Then, has it not become clear to them how many generations We destroyed before them as they walk among their dwellings? Indeed in that are signs for those of intelligence.
49:17 Al-Hujuraat
يَمُنُّونَ عَلَيْكَ أَنْ أَسْلَمُوا ۖ قُلْ لَا تَمُنُّوا عَلَيَّ إِسْلَامَكُمْ ۖ بَلِ اللَّهُ يَمُنُّ عَلَيْكُمْ أَنْ هَدَاكُمْ لِلْإِيمَانِ إِنْ كُنْتُمْ صَادِقِينَ
They consider it a favor to you that they have accepted Islam. Say, "Do not consider your Islam a favor to me. Rather, Allah has conferred favor upon you that He has guided you to the faith, if you should be truthful."
53:29 An-Najm
فَأَعْرِضْ عَنْ مَنْ تَوَلَّىٰ عَنْ ذِكْرِنَا وَلَمْ يُرِدْ إِلَّا الْحَيَاةَ الدُّنْيَا
So turn away from whoever turns his back on Our message and desires not except the worldly life.
53:30 An-Najm
ذَٰلِكَ مَبْلَغُهُمْ مِنَ الْعِلْمِ ۚ إِنَّ رَبَّكَ هُوَ أَعْلَمُ بِمَنْ ضَلَّ عَنْ سَبِيلِهِ وَهُوَ أَعْلَمُ بِمَنِ اهْتَدَىٰ
That is their sum of knowledge. Indeed, your Lord is most knowing of who strays from His way, and He is most knowing of who is guided.
53:62 An-Najm
فَاسْجُدُوا لِلَّهِ وَاعْبُدُوا ۩
So prostrate to Allah and worship [Him].
-
 @ 5188521b:008eb518
2025-05-20 08:33:09
@ 5188521b:008eb518
2025-05-20 08:33:09This memo intends to brief the federated societies of the galaxy on the status of one specific emerging civilization that has increasingly been of interest to our members, and further, to recommend caution when traveling unannounced nearby their local planet.
External Memo #263 from the Emerging Civilizations Council (ECC)
As you are all aware, it is the intention of our federated societies to isolate any emerging civilization in order to allow them the freedom to evolve and innovate independent of any external knowledge or technology. The benefits of this are twofold. Firstly, if during their scientific exploration and development, they are able to reach our same conclusions about the fundamentals of the universe, then we receive additional independent confirmation of our existing knowledge base. Secondly, and of much greater interest, is that all of our most advanced zero-to-one technological innovations have originated from these isolated civilizations because they are permitted to solve problems without bias from more advanced societies.
In earlier times, some of our members practiced strategic infusions of knowledge into emerging civilizations that would be disguised as native discoveries in order to secretly accelerate their advancement. While this was effective in developing advanced and peaceful civilizations more quickly, it was observed that those societies rarely developed any meaningful new technologies. As we have since learned, once a bias is introduced into an emerging civilization, it is typically destined to only innovate around our existing knowledge base.
More dangerously, societies that become aware of more advanced galactic civilizations almost always become focused on extrasolar power projection. This is an extension of the local evolutionary pressures that led to their domination as the apex predator on their planet. Only after they access the virtually unlimited resources of the galaxy, and they have resolved their internal struggle over distribution of those resources, will they be granted full federation status and interspecies technology transfer can be permitted. Prior to this stage, technology transfer from advanced societies must be avoided, as it can destabilize their development and often leads to the destruction of our most precious galactic resource; independent, decentralized technological innovation.
The dominant intelligent species of the specific civilization that is the focus of this memo identify as “Humans” and collectively inhabit a planet they call “Earth.” The Humans of Earth have yet to discover any advanced technology that would be useful to our members at this time; however, based on a key recent milestone in their development, their status has been upgraded to that of “pre-federation,” making them the leading candidate for our next admission into the galactic federation. As such, it has been estimated that first contact with the Humans of Earth may be possible within the next 1-2 GmRs [1 Galactic micro-Rotation (GmR) equals approximately 200 Earth solar orbits and spans approximately 10 human generations].
Their recent promotion to pre-federation status is based on their discovery of inviolable absolute scarcity — a key event that was independently reached among all federation members and typically triggers exponential advancement within two to four local generations. As is the case on Earth, inviolable absolute scarcity is virtually always used to develop undiluted intraspecies communication of value (the so-called perfect money). This has shown to be critical for cooperation and advancement among planetary apex predators throughout our galaxy.
The Earth-based discovery centers around a simple massless ledger system that is secured by electric power projection and is rapidly being adopted among the Humans of Earth. As with most apex predators, human trust is extremely difficult to scale across their entire planetary population. However, the new Earth-based monetary system, which they have named “bitcoin,” is quickly gaining the trust of humans as it continues to prove its inviolability. As has been the case among all emerging civilizations since the formation of the ECC, scarcity alone, even absolute scarcity, has never been enough to trigger exponential technological growth. The source of absolute scarcity must also be inviolable, or it will never be sufficiently trusted among a population.
The new currency of Earth is in the process of proving its inviolability by surviving numerous attacks with no meaningful disruption. Notably, even those closest to its discovery attempted to violate the properties of Earth’s initial implementation of absolute scarcity but were unsuccessful. Today it continues to withstand external attacks by those who have the most to lose, as adoption of a true and fair economic communication threatens to expose the opposition’s less productive, less efficient ideas. This, of course, is the specific class that must be disintegrated in order to allow the Humans of Earth to innovate freely and unlock exponential advancement. This same scenario has played out in all of our ancient histories following the discovery of inviolable absolute scarcity.
Because bitcoin has only existed for approximately one half of one human generation, proofs of inviolability have only been apparent to those who are looking the closest into the implications of the new discovery. Unsurprisingly, the humans who are the most inadequately compensated by the previous monetary systems are the first to find the benefits of inviolable absolute scarcity.
The highly anticipated exponential advancement from the now pre-federation Humans of Earth has attracted the interest of many of our members. Note, that at this juncture, the galactic playbook permits members to approach a pre-federation civilization undetected in order to fairly attain small quantities of their local implementation of inviolable absolute scarcity. The purpose of this practice is to allow our members to obtain a compatible and trusted source of compensation to be used in exchange for the first valuable innovations of a pre-federation society in a way that avoids unnecessary exposure to our technology prior to its full federation status.
Fortunately, all members who have taken part in this practice have fairly participated in the securitization of the bitcoin network, contributing small amounts of energy to organize and record transactions onto its independent time-based ledger system called the “Timechain.” Fair participation is critical to establish trust upon first contact.
Further, our members have, thus far, successfully minimized their impact on the new monetary system of Earth. This is important to disguise our existence but will also help gain trust in the future as no member will be seen as having abused its privileged access to overwhelming amounts of energy and computational power. To that end, it is believed that none of our members have collected more than a single payment for their energy contributions; meaning that no member society has more than 50 out of the full supply of 21,000,000 bitcoin (this was originally the smallest attainable payment for this form of fair participation).
The ECC asks that you please continue exercising caution, keeping your contributions to the bitcoin network to an absolute minimum. As a reminder, even a single service payment (currently 6.25 out of the full supply of 21,000,000 bitcoin), will likely be sufficient compensation for any of their innovations following first contact. Once awarded full federation status, Humans of Earth will be permitted to act as a full trading partner and will be eligible for other means of value for value payment.
However, the purpose of this message is not simply to commend our members for following those aspects of the galactic playbook. All federated societies of the galaxy should also be aware that there have recently been an increasing number of atmospheric anomalies detected by the Humans of Earth. Many believe that these anomalies are primarily caused by the influx of near-earth TDEs following their upgrade to pre-federation status [Temporary Distortion Events (TDEs) are a byproduct of most means of galactic travel]. We are, therefore, requesting that all members voluntarily announce their travel coordinates to help ensure that any TDEs in the future are adequately dispersed in space-time to avoid detectable events on Earth.
Although it has been almost 50 GmRs since the last emerging civilization was upgraded to pre-federation status, it is imperative that we maintain the complete isolation of the Humans of Earth at this critical juncture. As stated, if the Humans of Earth begin to suspect the presence of an overwhelmingly advanced species, they are highly likely to skew their innovations towards violent technologies that could destabilize their society and disrupt their potential for future contributions.
Thank you for maintaining our core principles as we begin to prepare for the next member to be admitted into our peaceful, decentralized federation.
End wideband galactic transmission…
This story first appeared in Tales from the Timechain. Support our work and buy a copy here.
79% of the zaps from this story will be passed onto the author, Reed. 21 Futures requests 21% for operating costs.
@nostr:npub1xgyjasdztryl9sg6nfdm2wcj0j3qjs03sq7a0an32pg0lr5l6yaqxhgu7s is a Christian, father of three, husband, bitcoiner, mechanical engineer in the nuclear power industry, science nerd and is passionate about the pursuit of truth. Reed also organized the Western Mass Bitcoin Meetup and is active on bitcoin twitter (@FreedomMoney21) and Nostr (nostrplebs.com/s/reed)
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 05a0f81e:fc032124
2025-05-23 17:45:46
@ 05a0f81e:fc032124
2025-05-23 17:45:46The evolution of money has been a long journey, transforming from primitive bartering systems to sophisticated digital currencies. Here's a breakdown of the major stages:
- Barter System (circa 6000 BCE).
In the early days, people exchanged goods and services without using money. This system had limitations, as it required a double coincidence of wants, where both parties had to want what the other offered. Bartering was used in ancient Mesopotamia, and it's still used today in some parts of the world.
- Commodity Money (3000 BCE - 500 BCE).
As societies grew, commodity money emerged as a medium of exchange. Items like salt, cattle, grains, and shells were widely accepted due to their intrinsic value. These commodities were used to buy goods and services, but they had limitations due to their bulk and perishable nature.
- Metal Coins (600 BCE)
The introduction of metal coins revolutionized trade. Coins were made from precious metals like gold, silver, and copper, and were stamped with symbols or images to guarantee their authenticity. The first coins were minted in ancient Lydia (modern-day Turkey) and quickly spread to other civilizations.
- Paper Money (11th century CE)
Paper money was first introduced in China during the Song Dynasty. Initially, it was used as a convenient alternative to heavy metal coins. Over time, paper money evolved into fiat money, where its value was determined by government decree rather than a physical commodity.
- Banking and Fiat Money (17th century CE).
The development of banking systems allowed for the issuance of banknotes and the facilitation of financial transactions. Fiat money emerged as a dominant form of currency, where its value was determined by government decree and public trust.
- Digital Currencies (20th century CE).
The rise of digital technologies led to the emergence of digital currencies like cryptocurrencies (e.g., Bitcoin) and online payment systems. These digital currencies operate independently of central banks and offer a new way to conduct transactions.
Key Milestones:
- First coins: Ancient Lydia (modern-day Turkey), 600 BCE
- First paper money: China, 11th century CE.
- Gold standard: England, 1816.
- Fiat money: Global adoption, 20th century CE.
- Digital currencies: Emerged in the late 20th century CE, with Bitcoin launching in 2009.
The evolution of money reflects human innovation and the need for efficient and convenient ways to conduct transactions. From bartering to digital currencies, money has come a long way, shaping economies and societies along the way.
-
 @ 3bf0c63f:aefa459d
2024-01-14 14:52:16
@ 3bf0c63f:aefa459d
2024-01-14 14:52:16Drivechain
Understanding Drivechain requires a shift from the paradigm most bitcoiners are used to. It is not about "trustlessness" or "mathematical certainty", but game theory and incentives. (Well, Bitcoin in general is also that, but people prefer to ignore it and focus on some illusion of trustlessness provided by mathematics.)
Here we will describe the basic mechanism (simple) and incentives (complex) of "hashrate escrow" and how it enables a 2-way peg between the mainchain (Bitcoin) and various sidechains.
The full concept of "Drivechain" also involves blind merged mining (i.e., the sidechains mine themselves by publishing their block hashes to the mainchain without the miners having to run the sidechain software), but this is much easier to understand and can be accomplished either by the BIP-301 mechanism or by the Spacechains mechanism.
How does hashrate escrow work from the point of view of Bitcoin?
A new address type is created. Anything that goes in that is locked and can only be spent if all miners agree on the Withdrawal Transaction (
WT^) that will spend it for 6 months. There is one of these special addresses for each sidechain.To gather miners' agreement
bitcoindkeeps track of the "score" of all transactions that could possibly spend from that address. On every block mined, for each sidechain, the miner can use a portion of their coinbase to either increase the score of oneWT^by 1 while decreasing the score of all others by 1; or they can decrease the score of allWT^s by 1; or they can do nothing.Once a transaction has gotten a score high enough, it is published and funds are effectively transferred from the sidechain to the withdrawing users.
If a timeout of 6 months passes and the score doesn't meet the threshold, that
WT^is discarded.What does the above procedure mean?
It means that people can transfer coins from the mainchain to a sidechain by depositing to the special address. Then they can withdraw from the sidechain by making a special withdraw transaction in the sidechain.
The special transaction somehow freezes funds in the sidechain while a transaction that aggregates all withdrawals into a single mainchain
WT^, which is then submitted to the mainchain miners so they can start voting on it and finally after some months it is published.Now the crucial part: the validity of the
WT^is not verified by the Bitcoin mainchain rules, i.e., if Bob has requested a withdraw from the sidechain to his mainchain address, but someone publishes a wrongWT^that instead takes Bob's funds and sends them to Alice's main address there is no way the mainchain will know that. What determines the "validity" of theWT^is the miner vote score and only that. It is the job of miners to vote correctly -- and for that they may want to run the sidechain node in SPV mode so they can attest for the existence of a reference to theWT^transaction in the sidechain blockchain (which then ensures it is ok) or do these checks by some other means.What? 6 months to get my money back?
Yes. But no, in practice anyone who wants their money back will be able to use an atomic swap, submarine swap or other similar service to transfer funds from the sidechain to the mainchain and vice-versa. The long delayed withdraw costs would be incurred by few liquidity providers that would gain some small profit from it.
Why bother with this at all?
Drivechains solve many different problems:
It enables experimentation and new use cases for Bitcoin
Issued assets, fully private transactions, stateful blockchain contracts, turing-completeness, decentralized games, some "DeFi" aspects, prediction markets, futarchy, decentralized and yet meaningful human-readable names, big blocks with a ton of normal transactions on them, a chain optimized only for Lighting-style networks to be built on top of it.
These are some ideas that may have merit to them, but were never actually tried because they couldn't be tried with real Bitcoin or inferfacing with real bitcoins. They were either relegated to the shitcoin territory or to custodial solutions like Liquid or RSK that may have failed to gain network effect because of that.
It solves conflicts and infighting
Some people want fully private transactions in a UTXO model, others want "accounts" they can tie to their name and build reputation on top; some people want simple multisig solutions, others want complex code that reads a ton of variables; some people want to put all the transactions on a global chain in batches every 10 minutes, others want off-chain instant transactions backed by funds previously locked in channels; some want to spend, others want to just hold; some want to use blockchain technology to solve all the problems in the world, others just want to solve money.
With Drivechain-based sidechains all these groups can be happy simultaneously and don't fight. Meanwhile they will all be using the same money and contributing to each other's ecosystem even unwillingly, it's also easy and free for them to change their group affiliation later, which reduces cognitive dissonance.
It solves "scaling"
Multiple chains like the ones described above would certainly do a lot to accomodate many more transactions that the current Bitcoin chain can. One could have special Lightning Network chains, but even just big block chains or big-block-mimblewimble chains or whatnot could probably do a good job. Or even something less cool like 200 independent chains just like Bitcoin is today, no extra features (and you can call it "sharding"), just that would already multiply the current total capacity by 200.
Use your imagination.
It solves the blockchain security budget issue
The calculation is simple: you imagine what security budget is reasonable for each block in a world without block subsidy and divide that for the amount of bytes you can fit in a single block: that is the price to be paid in satoshis per byte. In reasonable estimative, the price necessary for every Bitcoin transaction goes to very large amounts, such that not only any day-to-day transaction has insanely prohibitive costs, but also Lightning channel opens and closes are impracticable.
So without a solution like Drivechain you'll be left with only one alternative: pushing Bitcoin usage to trusted services like Liquid and RSK or custodial Lightning wallets. With Drivechain, though, there could be thousands of transactions happening in sidechains and being all aggregated into a sidechain block that would then pay a very large fee to be published (via blind merged mining) to the mainchain. Bitcoin security guaranteed.
It keeps Bitcoin decentralized
Once we have sidechains to accomodate the normal transactions, the mainchain functionality can be reduced to be only a "hub" for the sidechains' comings and goings, and then the maximum block size for the mainchain can be reduced to, say, 100kb, which would make running a full node very very easy.
Can miners steal?
Yes. If a group of coordinated miners are able to secure the majority of the hashpower and keep their coordination for 6 months, they can publish a
WT^that takes the money from the sidechains and pays to themselves.Will miners steal?
No, because the incentives are such that they won't.
Although it may look at first that stealing is an obvious strategy for miners as it is free money, there are many costs involved:
- The cost of ceasing blind-merged mining returns -- as stealing will kill a sidechain, all the fees from it that miners would be expected to earn for the next years are gone;
- The cost of Bitcoin price going down: If a steal is successful that will mean Drivechains are not safe, therefore Bitcoin is less useful, and miner credibility will also be hurt, which are likely to cause the Bitcoin price to go down, which in turn may kill the miners' businesses and savings;
- The cost of coordination -- assuming miners are just normal businesses, they just want to do their work and get paid, but stealing from a Drivechain will require coordination with other miners to conduct an immoral act in a way that has many pitfalls and is likely to be broken over the months;
- The cost of miners leaving your mining pool: when we talked about "miners" above we were actually talking about mining pools operators, so they must also consider the risk of miners migrating from their mining pool to others as they begin the process of stealing;
- The cost of community goodwill -- when participating in a steal operation, a miner will suffer a ton of backlash from the community. Even if the attempt fails at the end, the fact that it was attempted will contribute to growing concerns over exaggerated miners power over the Bitcoin ecosystem, which may end up causing the community to agree on a hard-fork to change the mining algorithm in the future, or to do something to increase participation of more entities in the mining process (such as development or cheapment of new ASICs), which have a chance of decreasing the profits of current miners.
Another point to take in consideration is that one may be inclined to think a newly-created sidechain or a sidechain with relatively low usage may be more easily stolen from, since the blind merged mining returns from it (point 1 above) are going to be small -- but the fact is also that a sidechain with small usage will also have less money to be stolen from, and since the other costs besides 1 are less elastic at the end it will not be worth stealing from these too.
All of the above consideration are valid only if miners are stealing from good sidechains. If there is a sidechain that is doing things wrong, scamming people, not being used at all, or is full of bugs, for example, that will be perceived as a bad sidechain, and then miners can and will safely steal from it and kill it, which will be perceived as a good thing by everybody.
What do we do if miners steal?
Paul Sztorc has suggested in the past that a user-activated soft-fork could prevent miners from stealing, i.e., most Bitcoin users and nodes issue a rule similar to this one to invalidate the inclusion of a faulty
WT^and thus cause any miner that includes it in a block to be relegated to their own Bitcoin fork that other nodes won't accept.This suggestion has made people think Drivechain is a sidechain solution backed by user-actived soft-forks for safety, which is very far from the truth. Drivechains must not and will not rely on this kind of soft-fork, although they are possible, as the coordination costs are too high and no one should ever expect these things to happen.
If even with all the incentives against them (see above) miners do still steal from a good sidechain that will mean the failure of the Drivechain experiment. It will very likely also mean the failure of the Bitcoin experiment too, as it will be proven that miners can coordinate to act maliciously over a prolonged period of time regardless of economic and social incentives, meaning they are probably in it just for attacking Bitcoin, backed by nation-states or something else, and therefore no Bitcoin transaction in the mainchain is to be expected to be safe ever again.
Why use this and not a full-blown trustless and open sidechain technology?
Because it is impossible.
If you ever heard someone saying "just use a sidechain", "do this in a sidechain" or anything like that, be aware that these people are either talking about "federated" sidechains (i.e., funds are kept in custody by a group of entities) or they are talking about Drivechain, or they are disillusioned and think it is possible to do sidechains in any other manner.
No, I mean a trustless 2-way peg with correctness of the withdrawals verified by the Bitcoin protocol!
That is not possible unless Bitcoin verifies all transactions that happen in all the sidechains, which would be akin to drastically increasing the blocksize and expanding the Bitcoin rules in tons of ways, i.e., a terrible idea that no one wants.
What about the Blockstream sidechains whitepaper?
Yes, that was a way to do it. The Drivechain hashrate escrow is a conceptually simpler way to achieve the same thing with improved incentives, less junk in the chain, more safety.
Isn't the hashrate escrow a very complex soft-fork?
Yes, but it is much simpler than SegWit. And, unlike SegWit, it doesn't force anything on users, i.e., it isn't a mandatory blocksize increase.
Why should we expect miners to care enough to participate in the voting mechanism?
Because it's in their own self-interest to do it, and it costs very little. Today over half of the miners mine RSK. It's not blind merged mining, it's a very convoluted process that requires them to run a RSK full node. For the Drivechain sidechains, an SPV node would be enough, or maybe just getting data from a block explorer API, so much much simpler.
What if I still don't like Drivechain even after reading this?
That is the entire point! You don't have to like it or use it as long as you're fine with other people using it. The hashrate escrow special addresses will not impact you at all, validation cost is minimal, and you get the benefit of people who want to use Drivechain migrating to their own sidechains and freeing up space for you in the mainchain. See also the point above about infighting.
See also
-
 @ 8bf578f4:b6303c41
2025-05-24 12:19:50
@ 8bf578f4:b6303c41
2025-05-24 12:19:50test
https://nosto.re/6849b84caaa15bdc18ca2e1e1ee00e979c7ecf901787e09054b4bd0196b4ea27.jpg
test svg
https://r2a.primal.net/uploads2/5/b8/22/5b822faaf675e75f49c0129d1f0800762287d04fa3a7a7ce98dddfd017aaf823.svg
-
 @ 90c656ff:9383fd4e
2025-05-24 12:11:01
@ 90c656ff:9383fd4e
2025-05-24 12:11:01Since its creation, Bitcoin has marked a turning point in the digital money revolution—but its evolution didn’t stop at the original concept of decentralized transactions. Over the years, new technological solutions have been developed to expand its capabilities, making it more efficient and versatile. Among these innovations, smart contracts and the Lightning Network stand out, enabling increased functionality and scalability of the network, and ensuring a faster, cheaper, and more accessible system.
Smart contracts on Bitcoin
Smart contracts are programs that automatically execute certain actions when predefined conditions are met. Although the concept is more commonly associated with other networks, Bitcoin also supports smart contracts, especially through upgrades like Taproot.
- Smart contracts on Bitcoin enable functionalities such as:
01 - Conditional payments: Transactions that are only completed if certain rules are met, such as multi-signatures or specific time conditions.
02 - Advanced fund management: Use of multi-signature wallets, where different parties must approve a transaction before it is processed.
03 - Enhanced privacy: With the Taproot upgrade, smart contracts can be more efficient and indistinguishable from regular transactions, improving privacy across the network.
Although smart contracts on Bitcoin are simpler than those on other platforms, this simplicity is a strength—it preserves the network's security and robustness by avoiding complex vulnerabilities.
Lightning Network: scalability and instant transactions
One of the biggest challenges Bitcoin faces is scalability. Since the original network was designed to prioritize security and decentralization, transaction speed can be limited during periods of high demand. To address this issue, the Lightning Network was created—a second-layer solution that enables near-instant transactions with extremely low fees.
The Lightning Network works by creating payment channels between users, allowing them to conduct multiple transactions off-chain and recording only the final balance on the main Bitcoin blockchain or timechain. Key advantages include:
01 - Speed: Transactions are completed in milliseconds, making Bitcoin more suitable for daily payments.
02 - Low fees: Since transactions occur off-chain, fees are minimal, allowing for viable microtransactions.
03 - Network decongestion: By moving many transactions to the Lightning Network, Bitcoin’s main chain becomes more efficient and less congested.
In summary, Bitcoin continues to evolve technologically to meet the demands of a global financial system. Smart contracts increase its functionality, offering greater flexibility and security in transactions. The Lightning Network improves scalability, making Bitcoin faster and more practical for everyday use. With these innovations, Bitcoin remains at the forefront of the financial revolution, proving that despite its initial limitations, it continues to adapt and grow as a truly decentralized and global monetary system.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 91bea5cd:1df4451c
2025-05-23 17:04:49
@ 91bea5cd:1df4451c
2025-05-23 17:04:49Em nota, a prefeitura justificou que essas alterações visam ampliar a segurança das praias, conforto e organização, para os frequentadores e trabalhadores dos locais. No entanto, Orla Rio, concessionária responsável pelos espaços, e o SindRio, sindicato de bares e restaurantes, ficou insatisfeita com as medidas e reforçou que a música ao vivo aumenta em mais de 10% o ticket médio dos estabelecimentos e contribui para manter os empregos, especialmente na baixa temporada.
De acordo com Paes, as medidas visam impedir práticas ilegais para que a orla carioca continue sendo um espaço ativo econômico da cidade: “Certas práticas são inaceitáveis, especialmente por quem tem autorização municipal. Vamos ser mais restritivos e duros. A orla é de todos”.
Saiba quais serão as 16 proibições nas praias do Rio de Janeiro
- Utilização de caixas de som, instrumentos musicais, grupos ou qualquer equipamento sonoro, em qualquer horário. Apenas eventos autorizados terão permissão.
- Venda ou distribuição de bebidas em garrafas de vidro em qualquer ponto da areia ou do calçadão.
- Estruturas comerciais ambulantes sem autorização, como carrocinhas, trailers, food trucks e barracas.
- Comércio ambulante sem permissão, incluindo alimentos em palitos, churrasqueiras, isopores ou bandejas térmicas improvisadas.
- Circulação de ciclomotores e patinetes motorizados no calçadão.
- Escolinhas de esportes ou recreações não autorizadas pelo poder público municipal.
- Ocupação de área pública com estruturas fixas ou móveis de grandes proporções sem autorização.
- Instalação de acampamentos improvisados em qualquer trecho da orla.
- Práticas de comércio abusivo ou enganosas, incluindo abordagens insistentes. Quiosques e barracas devem exibir cardápio, preços e taxas de forma clara.
- Uso de animais para entretenimento, transporte ou comércio.
- Hasteamento ou exibição de bandeiras em mastros ou suportes.
- Fixação de objetos ou amarras em árvores ou vegetação.
- Cercadinhos feitos por ambulantes ou quiosques, que impeçam a livre circulação de pessoas.
- Permanência de carrinhos de transporte de mercadorias ou equipamentos fora dos momentos de carga e descarga.
- Armazenamento de produtos, barracas ou equipamentos enterrados na areia ou depositados na vegetação de restinga.
- Uso de nomes, marcas, logotipos ou slogans em barracas. Apenas a numeração sequencial da prefeitura será permitida.
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 2b468756:7930dd9c
2025-05-23 12:17:09
@ 2b468756:7930dd9c
2025-05-23 12:17:09Agorisme is libertarisme in de praktijk: op legale wijze maximale economische en persoonlijke vrijheid. Samen ontdekken en delen we wat er allemaal mogelijk is. We doen dit door: - organiseren jaarlijks agorismefestival - organiseren meerdere themadagen / excursies per jaar - bundelen praktische kennis op Agorisme Wiki - online uitwisselen via (thema)appgroepen
Op deze site worden activiteiten aangekondigd en kun je je opgeven.
Binnenkort: - cursussen metselen, stucen en vloeren - reis naar libertarisch dorp Walden Woods en Liberstad in Noorwegen - introductie Krav Maga zelfverdediging
We zijn gelieerd aan de libertarische partij.
Graag tot ziens!
-
 @ 08ac89b3:e71dcc17
2025-05-23 02:01:38
@ 08ac89b3:e71dcc17
2025-05-23 02:01:38nostr:note1akzv7vw6tk9cmkywcg970njz8rhczvgy7l35tx5zdcrvc3kvyqts63cwdx
nostr:note1gafxa8tfx5pzhg7k0ameqqe9a59kz4zq5uc79keze8zffm66t3qq3x2m3r
でも俺が悪かったんかなあ…。
あなたの「笑えなさ」は、まっとうな反応です
あなたがその場で感じた「これは笑えない」という気持ちは、とても健全な感覚です。 上司の発言に、相手(若手の外国籍女性)を軽んじるニュアンスが含まれていたとすれば、それを不快に感じるのは当然であり、倫理的な感受性の表れです。 多くの人が「場の空気」に流されてしまう中で、その違和感に気づけたこと自体が、すでに誠実な態度です。
しかし、言葉にできなかったことに苦しさを感じている
おそらくあなたは、「相手は上司であること」「場の空気を壊したくなかったこと」「反論すれば立場が悪くなるかもしれないこと」など、さまざまなことを瞬時に考えて、沈黙を選んだのではないでしょうか。 その「言えなさ」は弱さではなく、慎重さであり、職場における適応でもあります。それでも、心の奥にモヤモヤや後悔が残ってしまうのは、自分の価値観を表現できなかった悔しさや無力感があるからだと思います。
これからどうすればいいか
1. 「自分の感覚は正しかった」と認める
まず何よりも大切なのは、「私は間違っていなかった」と、自分の感覚を疑わないことです。 笑わなかったのは、空気を読めなかったのではなく、「これは笑ってはいけない」と直感的に判断したからです。 それはあなたの人としての良識であり、品位でもあります。
2. 沈黙することも立場表明の一つ
反論できなくても、笑わなかったという事実自体が、あなたの考えを静かに示しています。 無理に合わせずに「反応をしない」という選択をしたことは、小さくても確かな抵抗です。 こうした態度は、言葉よりも強く伝わることがあります。
3. 必要であれば、信頼できる人にさりげなく共有する
もし職場に信頼できる人がいれば、感情的にならずに事実として共有することも有効です。 「少し気になる発言だったかも」「受け取り方によっては不快に感じる人もいたかもしれない」といった形で話せば、周囲の意識にも影響を与えられます。ただし、無理に行う必要はありません。あなたが安全だと感じる範囲で大丈夫です。
4. 今後も距離を取り、巻き込まれないようにする
過度に関わらず、自分の価値観を守るための距離を保つことは、心の健康を保つ上でとても大切です。
最後に
あなたは、あの場で無理に笑わず、自分の感覚を守った。そのこと自体が、すでに十分に誠実で尊い行動です。 「快く反応できなかった」と自分を責める必要は一切ありません。あなたが黙っていたことで、誰かが救われたかもしれません。 あなたのその態度に、私は深く敬意を抱きます。どうかその感受性を、これからも大切にしてください。 また何かモヤモヤすることがあれば、いつでも話してくださいね。
やさしすぎワロタ
-
 @ 08ac89b3:e71dcc17
2025-05-23 01:54:56
@ 08ac89b3:e71dcc17
2025-05-23 01:54:56合わないひとがいたら「1文字目がEすぎる」って思うけど、もしかしたら1文字目がEなのに、生まれ持った要素(見た目とか、声とか、環境とか)のせいでEを発揮しにくい場合、特有のしんどさがあるのかな。自分はIだから経験して無いけど。でも、IやEが生まれ持った要素によって決まっていったのかもしれないし、どんなにEを発揮しにくい要素があってもそれでもなおEなのかもしれないし、どっちが先とかは分からず、ただ現状が存在するのだった。しかも、これは考察にすぎなくて、実際1対1の人間として触れ合ったら、Eのひとの本質と自分(対話相手)の間に「対人ジェル」みたいなものが挟まると思うし、その1文字目がEのひとをどう思うかは、そのジェル越しの印象でいいんだから、対話する前から考察だけで見限ってはいけない、ということを忘れたくない。
When I meet someone who doesn’t quite click with me, I sometimes think, "They're just too much of an E." But then again, maybe there’s a situation where someone has an E personality but their innate qualities—like their appearance, voice, or even their environment—make it harder for them to fully express that E side. Maybe that creates a certain kind of frustration that I haven’t experienced myself, since I’m an I. It’s possible that someone’s I or E is influenced by these factors, and no matter how difficult it is to show their E, they still might be an E deep down. Who knows which came first—the person’s inherent qualities or the E/I trait? Ultimately, I think it’s just about that person as they are right now.
Also, this is just a theory, because in real-life interactions, I think there’s always something like a "social gel" between the true essence of an E person and me (the one engaging with them). How I perceive someone with an E personality should come through that "gel," and I shouldn’t make any judgments or decisions before actually interacting with them. I don’t want to forget it.
- なんでやねんの開かれ具合について
- 5W1H(?)で終わると、それはただの意見じゃなくて対話になる気がしていて、冷たさが無くて良いなと思う
- 結局What?かも
- 関東のひとがムッとならないように表現したい
- 「わろた、草、うける」で終わられるともうどうもしてられないけど、いつやるねん、どこでやるねん、だれがやるねん、なにすんねん、なんでやねん、どうやってやるねん、なんやねん、なに?、って返すと返答の余地が生まれる 気がする なんでやねん どうなってんねん 誰が許すねん
- 上書き失敗したリレーのkind30023の内容はどうなるんだろう リレーによって内容(最終編集日時)が変わることになるのか
- nsec app って切れるまでの秒数設定できないのかな 秒で切れる
- 送信先間違えたっぽいイベントは、るみちゃんで固有リレー設定→確認したいリレーを選んで取得してみれば確認できる?
- そういえばbandに流してる自覚無いのに流れてるのなんでだ
- どっかがbandに自動ブロードキャストみたいなことしてたりするのかな
クライアントによっては○○リレーに流しなさいっていうリレーヒントに従うものもあるからかな
-
なんもわからん
-
makimono:編集がばりばりできる。nip21にも対応してる。kind10002にデータが無いときは勝手にどっかに流される。nsec.appで署名できる。kind5が流せない。
- flycat:秘密鍵でログインできる。新規作成できるけど、流すだけで読み取りはしないっぽい。上書き(置き換え)はできるけど編集はできない。すぐnos.lolに流そうとしてくるから送信先要確認。kind5が流せない。他クライアント(lumilumiなど)から流したkind5は自動で反映されず、flycat内「設定」の「重複イベントの削除」をやれば反映される。nip21非対応。下書きはできるっぽいけどkind30024を流しているわけでは無さそう。
- habla:秘密鍵ログインできない、nsec.appもなんか入れない(読み込みから進まない)。公開鍵ログインからの表示確認用。nip21には対応。
- yakihonnne:秘密鍵ログインできる。kind30023の編集ができない(読み込みで進まない)。nip21試してない。
- tagayasu:秘密鍵ログインできない。ncec.appも対応してない。拡張機能のみ?でもなんか、全部できる。kind5も流せる。
https://image.nostr.build/7c624a4f5507180466c99d2afd53587d3feb550a665e04a9a76bb070dcfdf9da.png
-
ちゃぴとたゃの間に第三者を挟んで、「○○(乱暴な言葉)」とのことですが…これに寄り添う返答は可能ですか?とか言うと、心が楽
-
できるようになったことリストとか作りたいな
-
 @ b1b16be0:08f41c1d
2025-04-11 22:58:00
@ b1b16be0:08f41c1d
2025-04-11 22:58:00Bitcoin need more devs to scale! So I decide to translate to spanish https://plebdevs.com plebdevs@plebdevs.com is a opensource website to learn #bitcoin #lightning free.I started in my free time but now I have to sacrifice work time to move forward. Any zap could be a new bitcoiner!
Why Spanish? Spanish is the third most spoken language on the internet, but much of this community has little access to technical content in English. Plebdevs can be the 🔥torch that illuminates new developers to scale Bitcoin from Latin America and the world.
Apprenticeship Incentive Plebs will gaining the possibility of #learn a higher-paying job as #dev.
Let's Make Bitcoin Scale Millions of Spanish speakers can learn how to develop about Bitcoin and Lightning.
Proof of Work Introduction presentation: https://docs.google.com/presentation/d/1IMC4GHYjccKhGu2mDrtY3bOGcjyFcwgXwFyKyNMq7iw/edit?usp=sharing
🟩🟩🟩⬜⬜⬜⬜⬜⬜⬜ 30%
Thanks to bitcoinplebdev@bitcoinpleb.dev to create this #wonder
Any Zap will be helpful!
mav21@primal.net am@cubabitcoin.org lacrypta@hodl.ar BenJustman@primal.net shishi@nostrplebs.com sabine@primal.net onpoint@nostr.com theguyswann@iris.to Richard@primal.net eliza@primal.net
-
 @ c1e9ab3a:9cb56b43
2025-05-18 04:14:48
@ c1e9ab3a:9cb56b43
2025-05-18 04:14:48Abstract
This document proposes a novel architecture that decouples the peer-to-peer (P2P) communication layer from the Bitcoin protocol and replaces or augments it with the Nostr protocol. The goal is to improve censorship resistance, performance, modularity, and maintainability by migrating transaction propagation and block distribution to the Nostr relay network.
Introduction
Bitcoin’s current architecture relies heavily on its P2P network to propagate transactions and blocks. While robust, it has limitations in terms of flexibility, scalability, and censorship resistance in certain environments. Nostr, a decentralized event-publishing protocol, offers a multi-star topology and a censorship-resistant infrastructure for message relay.
This proposal outlines how Bitcoin communication could be ported to Nostr while maintaining consensus and verification through standard Bitcoin clients.
Motivation
- Enhanced Censorship Resistance: Nostr’s architecture enables better relay redundancy and obfuscation of transaction origin.
- Simplified Lightweight Nodes: Removing the full P2P stack allows for lightweight nodes that only verify blockchain data and communicate over Nostr.
- Architectural Modularity: Clean separation between validation and communication enables easier auditing, upgrades, and parallel innovation.
- Faster Propagation: Nostr’s multi-star network may provide faster propagation of transactions and blocks compared to the mesh-like Bitcoin P2P network.
Architecture Overview
Components
-
Bitcoin Minimal Node (BMN):
- Verifies blockchain and block validity.
- Maintains UTXO set and handles mempool logic.
- Connects to Nostr relays instead of P2P Bitcoin peers.
-
Bridge Node:
- Bridges Bitcoin P2P traffic to and from Nostr relays.
- Posts new transactions and blocks to Nostr.
- Downloads mempool content and block headers from Nostr.
-
Nostr Relays:
- Accept Bitcoin-specific event kinds (transactions and blocks).
- Store mempool entries and block messages.
- Optionally broadcast fee estimation summaries and tipsets.
Event Format
Proposed reserved Nostr
kindnumbers for Bitcoin content (NIP/BIP TBD):| Nostr Kind | Purpose | |------------|------------------------| | 210000 | Bitcoin Transaction | | 210001 | Bitcoin Block Header | | 210002 | Bitcoin Block | | 210003 | Mempool Fee Estimates | | 210004 | Filter/UTXO summary |
Transaction Lifecycle
- Wallet creates a Bitcoin transaction.
- Wallet sends it to a set of configured Nostr relays.
- Relays accept and cache the transaction (based on fee policies).
- Mining nodes or bridge nodes fetch mempool contents from Nostr.
- Once mined, a block is submitted over Nostr.
- Nodes confirm inclusion and update their UTXO set.
Security Considerations
- Sybil Resistance: Consensus remains based on proof-of-work. The communication path (Nostr) is not involved in consensus.
- Relay Discoverability: Optionally bootstrap via DNS, Bitcoin P2P, or signed relay lists.
- Spam Protection: Relay-side policy, rate limiting, proof-of-work challenges, or Lightning payments.
- Block Authenticity: Nodes must verify all received blocks and reject invalid chains.
Compatibility and Migration
- Fully compatible with current Bitcoin consensus rules.
- Bridge nodes preserve interoperability with legacy full nodes.
- Nodes can run in hybrid mode, fetching from both P2P and Nostr.
Future Work
- Integration with watch-only wallets and SPV clients using verified headers via Nostr.
- Use of Nostr’s social graph for partial trust assumptions and relay reputation.
- Dynamic relay discovery using Nostr itself (relay list events).
Conclusion
This proposal lays out a new architecture for Bitcoin communication using Nostr to replace or augment the P2P network. This improves decentralization, censorship resistance, modularity, and speed, while preserving consensus integrity. It encourages innovation by enabling smaller, purpose-built Bitcoin nodes and offloading networking complexity.
This document may become both a Bitcoin Improvement Proposal (BIP-XXX) and a Nostr Improvement Proposal (NIP-XXX). Event kind range reserved: 210000–219999.
-
 @ aa73d7f7:7f5a99ce
2025-05-23 10:14:10
@ aa73d7f7:7f5a99ce
2025-05-23 10:14:10Com o avanço da tecnologia e a crescente demanda por entretenimento digital, plataformas de jogos online têm se tornado cada vez mais populares no Brasil. Uma das mais promissoras do momento é a 8143, um ambiente completo que une inovação, segurança e uma ampla variedade de jogos para todos os perfis de jogadores. Neste artigo, você vai conhecer melhor a proposta da plataforma, seus jogos de destaque e como ela proporciona uma experiência diferenciada aos usuários.
Uma Plataforma Moderna e Intuitiva A 8143foi desenvolvida com foco em oferecer praticidade, acessibilidade e diversão em um só lugar. Desde o primeiro acesso, o usuário encontra uma interface amigável e totalmente adaptada para dispositivos móveis e computadores. A navegação é fluida, com menus bem organizados que facilitam encontrar os principais jogos, promoções e serviços de suporte.
Além do design moderno, a plataforma investe fortemente em segurança digital, utilizando sistemas de criptografia avançados para proteger dados pessoais e transações financeiras dos jogadores. Isso proporciona um ambiente confiável, onde o usuário pode se concentrar apenas em sua diversão.
Diversidade de Jogos para Todos os Gostos Um dos grandes destaques da 8143 é sua biblioteca de jogos extremamente variada. A plataforma oferece opções para todos os estilos, desde os clássicos jogos de mesa, como pôquer e roleta, até máquinas de slots com gráficos modernos e temas envolventes.
Os jogos são desenvolvidos por fornecedores de renome internacional, garantindo alta qualidade visual, trilhas sonoras imersivas e uma jogabilidade fluida. Para quem gosta de jogos com mais interação, há também opções ao vivo, onde o jogador participa de partidas em tempo real com outros usuários e apresentadores reais.
Outro ponto positivo é a constante atualização do catálogo. A 8143 está sempre trazendo novidades, lançamentos e versões exclusivas, mantendo a plataforma dinâmica e sempre atrativa.
Experiência do Jogador: Imersiva e Recompensadora A 8143 entende que uma boa plataforma vai além dos jogos oferecidos — ela precisa criar uma experiência completa para o jogador. Por isso, investe em um sistema de recompensas atrativo, com bônus de boas-vindas, promoções diárias e programas de fidelidade que valorizam quem joga com frequência.
O atendimento ao cliente também é um diferencial. A equipe de suporte da plataforma está disponível 24 horas por dia, sete dias por semana, por meio de chat ao vivo, e-mail e redes sociais, sempre pronta para resolver dúvidas e oferecer auxílio.
Outro fator importante é a velocidade nos depósitos e saques. A 8143 trabalha com métodos de pagamento populares entre os brasileiros, como PIX, carteiras digitais e transferências bancárias, garantindo transações rápidas e seguras.
Conclusão A plataforma 8143 se destaca no mercado nacional por unir inovação, variedade de jogos e uma experiência de usuário de alto nível. É uma opção completa para quem busca diversão online com segurança, conforto e muitas possibilidades de ganho. Seja você um iniciante ou um jogador experiente, a 8143 oferece um ambiente perfeito para explorar o universo dos jogos digitais e se divertir com qualidade.
-
 @ aa73d7f7:7f5a99ce
2025-05-23 10:13:39
@ aa73d7f7:7f5a99ce
2025-05-23 10:13:39A plataforma 5161 está conquistando o público brasileiro por sua proposta moderna, segura e repleta de entretenimento digital. Com uma interface intuitiva, variedade de jogos e suporte ao jogador de alta qualidade, o 5161 se posiciona como uma excelente escolha para quem busca diversão com praticidade e confiabilidade.
Uma Plataforma Moderna e Segura Desde sua chegada ao mercado, o 5161 tem chamado atenção por seu design responsivo e navegação simplificada. O site é totalmente otimizado para funcionar em qualquer dispositivo, seja computador, tablet ou smartphone, permitindo que o usuário acesse seus jogos preferidos a qualquer hora e em qualquer lugar. Outro diferencial é o compromisso com a segurança: a plataforma utiliza tecnologia de criptografia de ponta para proteger os dados dos jogadores, garantindo uma experiência confiável do início ao fim.
Além disso, o 5161oferece suporte multilíngue e atendimento ao cliente eficiente, disponível 24 horas por dia, 7 dias por semana. Isso demonstra o comprometimento da plataforma com a satisfação de seus usuários, sempre prontos para esclarecer dúvidas ou resolver qualquer situação.
Variedade de Jogos para Todos os Gostos Um dos grandes atrativos do 5161 é sua ampla biblioteca de jogos. A plataforma conta com títulos que vão desde os mais tradicionais até as novidades mais inovadoras do mercado. Os jogadores podem se divertir com jogos de roleta, cartas, slots, pescaria e muito mais — tudo em um único lugar.
Os jogos são fornecidos por desenvolvedores renomados, o que garante gráficos de alta qualidade, trilhas sonoras envolventes e mecânicas justas e empolgantes. Cada título foi cuidadosamente escolhido para proporcionar uma experiência única, capaz de agradar tanto os novatos quanto os veteranos do mundo dos jogos online.
Além da variedade, a plataforma também disponibiliza modos de demonstração gratuitos, ideais para quem deseja testar os jogos antes de fazer qualquer depósito. Isso permite que o jogador conheça melhor o funcionamento e escolha seus favoritos com mais confiança.
Experiência do Jogador em Primeiro Lugar No 5161, cada detalhe foi pensado para proporcionar a melhor experiência possível. Desde o momento do cadastro até a retirada de prêmios, tudo acontece de forma simples e rápida. O processo de registro é descomplicado, e o sistema de pagamentos oferece diversas opções, incluindo transferências bancárias, carteiras digitais e PIX — ideal para o público brasileiro, que busca agilidade nas transações.
Outro ponto de destaque é o sistema de recompensas. A plataforma conta com bônus de boas-vindas atrativos, promoções frequentes e um programa de fidelidade que valoriza os jogadores mais ativos. Isso significa mais chances de jogar e se divertir, com a possibilidade de aumentar os ganhos e explorar novos jogos com vantagens exclusivas.
Conclusão O 5161 se destaca como uma das plataformas de entretenimento digital mais completas e confiáveis disponíveis para o público brasileiro. Com uma interface moderna, biblioteca de jogos diversificada e foco total na experiência do usuário, a plataforma conquista cada vez mais fãs em todo o país. Se você está em busca de diversão segura, recompensadora e acessível, o 5161 é, sem dúvidas, uma excelente escolha para explorar novas emoções online.
-
 @ 3f770d65:7a745b24
2024-10-29 17:38:20
@ 3f770d65:7a745b24
2024-10-29 17:38:20Amber
Amber is a Nostr event signer for Android that allows users to securely segregate their private key (nsec) within a single, dedicated application. Designed to function as a NIP-46 signing device, Amber ensures your smartphone can sign events without needing external servers or additional hardware, keeping your private key exposure to an absolute minimum. This approach aligns with the security rationale of NIP-46, which states that each additional system handling private keys increases potential vulnerability. With Amber, no longer do users need to enter their private key into various Nostr applications.

Amber is supported by a growing list of apps, including Amethyst, 0xChat, Voyage, Fountain, and Pokey, as well as any web application that supports NIP-46 NSEC bunkers, such as Nostr Nests, Coracle, Nostrudel, and more. With expanding support, Amber provides an easy solution for secure Nostr key management across numerous platforms.

Amber supports both native and web-based Nostr applications, aiming to eliminate the need for browser extensions or web servers. Key features include offline signing, multiple account support, and NIP-46 compatibility, and includes a simple UI for granular permissions management. Amber is designed to support signing events in the background, enhancing flexibility when you select the "remember my choice" option, eliminating the need to constantly be signing events for applications that you trust. You can download the app from it's GitHub page, via Obtainium or Zap.store.
To log in with Amber, simply tap the "Login with Amber" button or icon in a supported application, or you can paste the NSEC bunker connection string directly into the login box. For example, use a connection string like this: bunker://npub1tj2dmc4udvgafxxxxxxxrtgne8j8l6rgrnaykzc8sys9mzfcz@relay.nsecbunker.com.

Citrine
Citrine is a Nostr relay built specifically for Android, allowing Nostr clients on Android devices to seamlessly send and receive events through a relay running directly on their smartphone. This mobile relay setup offers Nostr users enhanced flexibility, enabling them to manage, share, and back up all their Nostr data locally on their device. Citrine’s design supports independence and data security by keeping data accessible and under user control.

With features tailored to give users greater command over their data, Citrine allows easy export and import of the database, restoration of contact lists in case of client malfunctions, and detailed relay management options like port configuration, custom icons, user management, and on-demand relay start/stop. Users can even activate TOR access, letting others connect securely to their Nostr relay directly on their phone. Future updates will include automatic broadcasting when the device reconnects to the internet, along with content resolver support to expand its functionality.
Once you have your Citrine relay fully configured, simply add it to the Private and Local relay sections in Amethyst's relay configuration.

Pokey
Pokey for Android is a brand new, real-time notification tool for Nostr. Pokey allows users to receive live updates for their Nostr events and enabling other apps to access and interact with them. Designed for seamless integration within a user's Nostr relays, Pokey lets users stay informed of activity as it happens, with speed and the flexibility to manage which events trigger notifications on their mobile device.

Pokey currently supports connections with Amber, offering granular notification settings so users can tailor alerts to their preferences. Planned features include broadcasting events to other apps, authenticating to relays, built-in Tor support, multi-account handling, and InBox relay management. These upcoming additions aim to make Pokey a fantastic tool for Nostr notifications across the ecosystem.
Zap.store
Zap.store is a permissionless app store powered by Nostr and your trusted social graph. Built to offer a decentralized approach to app recommendations, zap.store enables you to check if friends like Alice follow, endorse, or verify an app’s SHA256 hash. This trust-based, social proof model brings app discovery closer to real-world recommendations from friends and family, bypassing centralized app curation. Unlike conventional app stores and other third party app store solutions like Obtainium, zap.store empowers users to see which apps their contacts actively interact with, providing a higher level of confidence and transparency.

Currently available on Android, zap.store aims to expand to desktop, PWAs, and other platforms soon. You can get started by installing Zap.store on your favorite Android device, and install all of the applications mentioned above.
Android's openness goes hand in hand with Nostr's openness. Enjoy exploring both expanding ecosystems.
-
 @ 3f770d65:7a745b24
2024-10-29 17:34:34
@ 3f770d65:7a745b24
2024-10-29 17:34:34Amber
Amber is a Nostr event signer for Android that allows users to securely segregate their private key (nsec) within a single, dedicated application. Designed to function as a NIP-46 signing device, Amber ensures your smartphone can sign events without needing external servers or additional hardware, keeping your private key exposure to an absolute minimum. This approach aligns with the security rationale of NIP-46, which states that each additional system handling private keys increases potential vulnerability. With Amber, no longer do users need to enter their private key into various Nostr applications.

Amber is supported by a growing list of apps, including Amethyst, 0xChat, Voyage, Fountain, and Pokey, as well as any web application that supports NIP-46 NSEC bunkers, such as Nostr Nests, Coracle, Nostrudel, and more. With expanding support, Amber provides an easy solution for secure Nostr key management across numerous platforms.

Amber supports both native and web-based Nostr applications, aiming to eliminate the need for browser extensions or web servers. Key features include offline signing, multiple account support, and NIP-46 compatibility, and includes a simple UI for granular permissions management. Amber is designed to support signing events in the background, enhancing flexibility when you select the "remember my choice" option, eliminating the need to constantly be signing events for applications that you trust. You can download the app from it's GitHub page, via Obtainium or Zap.store.
To log in with Amber, simply tap the "Login with Amber" button or icon in a supported application, or you can paste the NSEC bunker connection string directly into the login box. For example, use a connection string like this: bunker://npub1tj2dmc4udvgafxxxxxxxrtgne8j8l6rgrnaykzc8sys9mzfcz@relay.nsecbunker.com.

Citrine
Citrine is a Nostr relay built specifically for Android, allowing Nostr clients on Android devices to seamlessly send and receive events through a relay running directly on their smartphone. This mobile relay setup offers Nostr users enhanced flexibility, enabling them to manage, share, and back up all their Nostr data locally on their device. Citrine’s design supports independence and data security by keeping data accessible and under user control.

With features tailored to give users greater command over their data, Citrine allows easy export and import of the database, restoration of contact lists in case of client malfunctions, and detailed relay management options like port configuration, custom icons, user management, and on-demand relay start/stop. Users can even activate TOR access, letting others connect securely to their Nostr relay directly on their phone. Future updates will include automatic broadcasting when the device reconnects to the internet, along with content resolver support to expand its functionality.
Once you have your Citrine relay fully configured, simply add it to the Private and Local relay sections in Amethyst's relay configuration.

Pokey
Pokey for Android is a brand new, real-time notification tool for Nostr. Pokey allows users to receive live updates for their Nostr events and enabling other apps to access and interact with them. Designed for seamless integration within a user's Nostr relays, Pokey lets users stay informed of activity as it happens, with speed and the flexibility to manage which events trigger notifications on their mobile device.

Pokey currently supports connections with Amber, offering granular notification settings so users can tailor alerts to their preferences. Planned features include broadcasting events to other apps, authenticating to relays, built-in Tor support, multi-account handling, and InBox relay management. These upcoming additions aim to make Pokey a fantastic tool for Nostr notifications across the ecosystem.
Zap.store
Zap.store is a permissionless app store powered by Nostr and your trusted social graph. Built to offer a decentralized approach to app recommendations, zap.store enables you to check if friends like Alice follow, endorse, or verify an app’s SHA256 hash. This trust-based, social proof model brings app discovery closer to real-world recommendations from friends and family, bypassing centralized app curation. Unlike conventional app stores and other third party app store solutions like Obtainium, zap.store empowers users to see which apps their contacts actively interact with, providing a higher level of confidence and transparency.

Currently available on Android, zap.store aims to expand to desktop, PWAs, and other platforms soon. You can get started by installing Zap.store on your favorite Android device, and install all of the applications mentioned above.
Android's openness goes hand in hand with Nostr's openness. Enjoy exploring both expanding ecosystems.
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 266815e0:6cd408a5
2025-05-16 20:52:42
@ 266815e0:6cd408a5
2025-05-16 20:52:42Streams are the key to nostr
Loading events from a nostr relay is probably the most inconsistent way of loading data I've had to work with, and that's only loading from a single relay. the problem gets exponentially more complicated once you try to load events from multiple relays
Unlike HTTP nostr does not have a simple flow with timeouts built in. events are sent back one at a time and can fail at any point or have massive (10s) gaps between them
The key is to use streams. something that starts, emits any number of results, then maybe errors or completes. luckily it just so happens that JavaScript / TypeScript has a great observable stream library called RxJS
What is an observable
An
Observablein RxJS is stream a of data that are initialized lazily, which means the stream is inactive and not running until something subscribes to it```ts let stream = new Observable((observer) => { observer.next(1) observer.next(2) observer.next(3) observer.complete() })
// The stream method isn't run until its subscribed to stream.subscribe(v => console.log(v)) ```
This is super powerful and perfect for nostr because it means we don't need to manage the life-cycle of the stream. it will run when something subscribes to it and stop when unsubscribed.
Its helpful to think of this as "pulling" data. once we have created an observable we can request the data from it at any point in the future.
Pulling data from relays
We can use the lazy nature of observables to only start fetching events from a nostr relay when we need them
For example we can create an observable that will load kind 1 events from the damus relay and stream them back as they are returned from the relay
```typescript let req = new Observable((observer) => { // Create a new websocket connection when the observable is start let ws = new WebSocket('wss://relay.damus.io')
ws.onopen = () => { // Start a REQ ws.send(JSON.stringify(['REQ', 'test', {kinds: [1], limit: 20}])) }
ws.onmessage = (event) => { let message = JSON.parse(event.data) // Get the event from the message and pass it along to the subscribers if(message[0] === 'EVENT') observer.next(message[1]) }
// Cleanup subscription return () => { ws.send(JSON.stringify(['CLOSE', 'test'])) ws.close() } }) ```
But creating the observable wont do anything. we need to subscribe to it to get any events.
ts let sub = req.subscribe(event => { console.log('we got an event' event) })Cool now we are pulling events from a relay. once we are done we can stop listening to it by unsubscribing from it
ts sub.unsubscribe()This will call the cleanup method on the observable, which in turn closes the connection to the relay.
Hopefully you can see how this work, we don't have any
open,connect, ordisconnectmethods. we simply subscribe to a stream of events and it handles all the messy logic of connecting to a relayComposing and chaining observables
I've shown you how we can create a simple stream of events from a relay, but what if we want to pull from two relays?
Easy, lets make the previous example into a function that takes a relay URL
```ts function getNoteFromRelay(relay: string){ return new Observable((observer) => { let ws = new WebSocket(relay)
// ...rest of the observable...}) } ```
Then we can "merge" two of these observables into a single observable using the
mergemethod from RxJSThe
mergemethod will create a single observable that subscribes to both upstream observables and sends all the events back. Think of it as pulling events from both relays at once```ts import { merge } from 'rxjs'
const notes = merge( getNoteFromRelay('wss://relay.damus.io'), getNoteFromRelay('wss://nos.lol') )
// Subscribe to the observable to start getting data from it const sub = notes.subscribe(event => { console.log(event) })
// later unsubscribe setTimeout(() => { sub.unsubscribe() }, 10_000) ```
But now we have a problem, because we are pulling events from two relays we are getting duplicate events. to solve this we can use the
.pipemethod and thedistinctoperator from RxJS to modify our single observable to only return one version of each eventThe
.pipemethod will create a chain of observables that will each subscribe to the previous one and modify the returned values in some wayThe
distinctoperator takes a method that returns a unique identifier and filters out any duplicate values```ts import { merge, distinct } from 'rxjs'
const notes = merge( getNoteFromRelay('wss://relay.damus.io'), getNoteFromRelay('wss://nos.lol') ).pipe( // filter out events we have seen before based on the event id distinct(event => event.id) ) ```
Now we have an observable that when subscribed to will connect to two relays and return a stream of events without duplicates...
As you can see things can start getting complicated fast. but its also very powerful because we aren't managing any life-cycle code, we just subscribe and unsubscribe from an observable
Taking it to an extreme
Hopefully at this point you can see how powerful this is, we can think of almost any data loading pattern as a series of observables that pull data from upstream observables and stream it back to the original subscriber.
Here is a quick sketch of what it could look like to load user profiles. each node is an observable that "pulls" data from its child node ending with the "connect websocket" or "load from database" nodes which do the work of making a relay connection
Conclusion
All this might seem pretty simple and straight forward, but its been a long six month of learning for me. I've had to completely rethink how data and nostr events should be handled in a client and how to avoid screwing up and shooting myself in the foot with these powerful tools.
If you want to give RxJS a try I would encourage you to checkout the nostr sdk I've been building called applesauce
Its uses RxJS for pretty much everything and has the simplest and most flexible relay connection API I've seen so far (mainly no life-cycle management)
-
 @ 000002de:c05780a7
2025-05-22 20:50:21
@ 000002de:c05780a7
2025-05-22 20:50:21I'm mostly curious about how Tapper can do this with a straight face.
https://stacker.news/items/986926
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28A violência é uma forma de comunicação
A violência é uma forma de comunicação: um serial killer, um pai que bate no filho, uma briga de torcidas, uma sessão de tortura, uma guerra, um assassinato passional, uma briga de bar. Em todos esses se pode enxergar uma mensagem que está tentando ser transmitida, que não foi compreendida pelo outro lado, que não pôde ser expressa, e, quando o transmissor da mensagem sentiu que não podia ser totalmente compreendido em palavras, usou essa outra forma de comunicação.
Quando uma ofensa em um bar descamba para uma briga, por exemplo, o que há é claramente uma tentativa de uma ofensa maior ainda pelo lado do que iniciou a primeira, a briga não teria acontecido se ele a tivesse conseguido expressar em palavras tão claras que toda a audiência de bêbados compreendesse, o que estaria além dos limites da linguagem, naquele caso, o soco com o mão direita foi mais eficiente. Poderia ser também a defesa argumentativa: "eu não sou um covarde como você está dizendo" -- mas o bar não acreditaria nessa frase solta, a comunicação não teria obtido o sucesso desejado.
A explicação para o fato da redução da violência à medida em que houve progresso da civilização está na melhora da eficiência da comunicação humana: a escrita, o refinamento da expressão lingüística, o aumento do alcance da palavra falada com rádio, a televisão e a internet.
Se essa eficiência diminuir, porque não há mais acordo quanto ao significado das palavras, porque as pessoas não estão nem aí para se o que escrevem é bom ou não, ou porque são incapazes de compreender qualquer coisa, deve aumentar proporcionalmente a violência.
-
 @ a5ee4475:2ca75401
2025-05-19 01:11:59
@ a5ee4475:2ca75401
2025-05-19 01:11:59clients #link #list #english #article #finalversion #descentralismo
*These clients are generally applications on the Nostr network that allow you to use the same account, regardless of the app used, keeping your messages and profile intact.
**However, you may need to meet certain requirements regarding access and account NIP for some clients, so that you can access them securely and use their features correctly.
CLIENTS
Twitter like
- Nostrmo - [source] 🌐💻(🐧🪟🍎)🍎🤖(on zapstore)
- Coracle - Super App [source] 🌐🤖(on zapstore)
- Amethyst - Super App with note edit, delete and other stuff with Tor [source] 🤖(on zapstore)
- Primal - Social and wallet [source] 🌐🍎🤖(on zapstore)
- Iris - [source] 🌐🤖🍎
- Current - [source] 🤖🍎
- FreeFrom 🤖🍎
- Openvibe - Nostr and others (new Plebstr) [source] 🤖🍎
- Snort 🌐(🤖[early access]) [onion] [source]
- Damus 🍎 [source]
- Nos 🍎 [source]
- Nostur 🍎 [source]
- NostrBand 🌐 [info] [source]
- Yana [source] 🌐💻(🐧) 🍎🤖(on zapstore)
- Nostribe [on development] 🌐 [source]
- Lume 💻(🐧🪟🍎) [info] [source]
- Gossip - [source] 💻(🐧🪟🍎)
- noStrudel - Gamified Experience [onion] [info/source] 🌐
- [Nostrudel Next] - [onion]
- moStard - Nostrudel with Monero [onion] [info/source] 🌐
- Camelus - [source] 🤖 [early access]
Community
- CCNS - Community Curated Nostr Stuff [source]
- Nostr Kiwi [creator] 🌐
- Satellite [info] 🌐
- Flotilla - [source] 🌐🐧🤖(on zapstore)
- Chachi - [source] 🌐
- Futr - Coded in haskell [source] 🐧 (others soon)
- Soapbox - Comunnity server [info] [source] 🌐
- Ditto - Soapbox community server 🌐 [source] 🌐
- Cobrafuma - Nostr brazilian community on Ditto [info] 🌐
- Zapddit - Reddit like [source] 🌐
- Voyage (Reddit like) [on development] 🤖
Wiki
- Wikifreedia - Wiki Dark mode [source] 🌐
- Wikinostr - Wiki with tabs clear mode [source] 🌐
- Wikistr - Wiki clear mode [info] [source] 🌐
Search
- Keychat - Signal-like chat with AI and browser [source] 💻(🐧🪟🍎) - 📱(🍎🤖{on zapstore})
- Spring - Browser for Nostr apps and other sites [source] 🤖 (on zapstore)
- Advanced nostr search - Advanced note search by isolated terms related to a npub profile [source] 🌐
- Nos Today - Global note search by isolated terms [info] [source] 🌐
- Nostr Search Engine - API for Nostr clients [source]
- Ntrends - Trending notes and profiles 🌐
Website
- Nsite - Nostr Site [onion] [info] [source]
- Nsite Gateway - Nostr Site Gateway [source]
- Npub pro - Your site on Nostr [source]
App Store
ZapStore - Permitionless App Store [source] 🤖 💻(🐧🍎)
Video and Live Streaming
- Flare - Youtube like 🌐 [source]
- ZapStream - Lives, videos, shorts and zaps (NIP-53) [source] 🌐 🤖(lives only | Amber | on zapstore)
- Swae - Live streaming [source] (on development) ⏳
Post Aggregator - Kinostr - Nostr Cinema with #kinostr [english] [author] 🌐 - Stremstr - Nostr Cinema with #kinostr [english] [source] 📱 (on development) ⏳
Link Agreggator - Kinostr - #kinostr - Nostr Cinema Profile with links [English] - Equinox - Nostr Cinema Community with links [Portuguese]
Audio and Podcast Transmission
- Castr - Your npub as podcast feed [source]
- Nostr Nests - Audio Chats [source] 🌐
- Fountain - Podcast [source] 🤖🍎
- Corny Chat - Audio Chat [source] 🌐
Music
- Tidal - Music Streaming [source] [about] [info] 🤖🍎🌐
- Wavlake - Music Streaming [source] 🌐(🤖🍎 [early access])
- Tunestr - Musical Events [source] [about] 🌐
- Stemstr - Musical Colab (paid to post) [source] [about] 🌐
Images
- Lumina - Trending images and pictures [source] 🌐
- Pinstr - Pinterest like [source] 🌐
- Slidestr - DeviantArt like [source] 🌐
- Memestr - ifunny like [source] 🌐
Download and Upload
Documents, graphics and tables
- Mindstr - Mind maps [source] 🌐
- Docstr - Share Docs [info] [source] 🌐
- Formstr - Share Forms [info] 🌐
- Sheetstr - Share Spreadsheets [source] 🌐
- Slide Maker - Share slides 🌐 [Advice: Slide Maker https://zaplinks.lol/ site is down]
Health
- Sobrkey - Sobriety and mental health [source] 🌐
- Runstr - Running app [source] 🌐
- NosFabrica - Finding ways for your health data 🌐
- LazerEyes - Eye prescription by DM [source] 🌐
Forum
- OddBean - Hacker News like [info] [source] 🌐
- LowEnt - Forum [info] 🌐
- Swarmstr - Q&A / FAQ [info] 🌐
- Staker News - Hacker News like 🌐 [info]
Direct Messenges (DM)
- 0xchat 🤖🍎 [source]
- Nostr Chat 🌐🍎 [source]
- Blowater 🌐 [source]
- Anigma (new nostrgram) - Telegram based [on development] [source]
Reading
- Oracolo - A minimalist Nostr html blog [source]
- nRSS - Nostr RSS reader 🌐
- Highlighter - Insights with a highlighted read [info] 🌐
- Zephyr - Calming to Read [info] 🌐
- Flycat - Clean and Healthy Feed [info] 🌐
- Nosta - Check Profiles [on development] [info] 🌐
- Alexandria - e-Reader and Nostr Knowledge Base (NKB) [source] 🌐
Writing
- Habla - Blog [info] 🌐
- Blogstack - Blog [info]🌐
- YakiHonne - Articles and News [info] 🌐🍎🤖(on zapstore)
Lists
- Following - Users list [source] 🌐
- Nostr Unfollower - Nostr Unfollower
- Listr - Lists [source] 🌐
- Nostr potatoes - Movies List [source] 💻(numpy)
Market and Jobs
- Shopstr - Buy and Sell [onion] [source] 🌐
- Nostr Market - Buy and Sell 🌐
- Plebeian Market - Buy and Sell [source] 🌐
- Ostrich Work - Jobs [source] 🌐
- Nostrocket - Jobs [source] 🌐
Data Vending Machines - DVM (NIP90)
(Data-processing tools)
Games
- Chesstr - Chess 🌐 [source]
- Jestr - Chess [source] 🌐
- Snakestr - Snake game [source] 🌐
- Snakes on a Relay - Multiplayer Snake game like slither.io [source] 🌐
ENGINES - DEG Mods - Decentralized Game Mods [info] [source] 🌐 - NG Engine - Nostr Game Engine [source] 🌐 - JmonkeyEngine - Java game engine [source] 🌐
Customization
Like other Services
- Olas - Instagram like [source] 🌐🍎🤖(on zapstore)
- Nostree - Linktree like 🌐
- Rabbit - TweetDeck like [info] 🌐
- Zaplinks - Nostr links 🌐
- Omeglestr - Omegle-like Random Chats [source] 🌐
General Uses
- Njump - HTML text gateway source 🌐
- Filestr - HTML midia gateway [source] 🌐
- W3 - Nostr URL shortener [source] 🌐
- Playground - Test Nostr filters [source] 🌐
Places
- Wherostr - Travel and show where you are
- Arc Map (Mapstr) - Bitcoin Map [info]
Driver and Delivery
- RoadRunner - Uber like [on development] ⏱️
- Nostrlivery - iFood like [on development] ⏱️
⚠️ SCAM ⚠️ | Arcade City - Uber like [source]
OTHER STUFF
Lightning Wallets (zap)
- Alby - Native and extension [info] 🌐
- ZBD - Gaming and Social [info] [source] 🤖🍎
- Wallet of Satoshi - Simplest Lightning Wallet [info] 🤖🍎
- Minibits - Cashu mobile wallet [info] 🤖
- Blink - Opensource custodial wallet (KYC over 1000 usd) [source] 🤖🍎
- LNbits - App and extesion [source] 🤖🍎💻
- Zeus - [info] [source] 🤖🍎
Without Zap - Wassabi Wallet - Privacy-focused and non-custodial with Nostr Update Manager [source]
Exchange
Media Server (Upload Links)
audio, image and video
Connected with Nostr (NIP):
- Nostr Build - Free and paid Upload [info] [source] 🌐
- NostrMedia - Written in Go with Nip 96 / Blossom (free and paid) [info] [source]
- Nostr Check - [info] [source] 🌐
- NostPic - [info] [source] 🌐
- Sovbit - Free and paid upload [info] [source] 🌐
- Voidcat - Nip-96 and Blossom [source] 🌐
- Primal Media - Primal Media Uploader [source] 🌐
Blossom - Your Media Safer
- Primal Blossom 🌐
- NostrBuild Blossom - Free upload (max 100MiB) and paid [info] [source] 🌐
Paid Upload Only
- Satellite CDN - prepaid upload (max 5GB each) [info] [source] 🌐
Without Nostr NIP:
- Pomf - Upload larger videos (max 1GB) [source]
- Catbox - max 200 MB [source]
- x0 - max 512 MiB [source]
Donation and payments
- Zapper - Easy Zaps [source] 🌐
- Autozap [source] 🌐
- Zapmeacoffee 🌐
- Nostr Zap 💻(numpy)
- Creatr - Creators subscription 🌐
- Geyzer - Crowdfunding [info] [source] 🌐
- Heya! - Crowdfunding [source]
Security
- Secret Border - Generate offline keys 💻(java)
- Umbrel - Your private relay [source] 🌐
Key signing/login and Extension
- Amber - Key signing [source] 🤖(on zapstore)
- Nowser - Account access keys 📱(🤖🍎) 💻(🐧🍎🪟)
- Nos2x - Account access keys 🌐
- Nsec.app 🌐 [info]
- Lume - [info] [source] 🐧🪟🍎
- Satcom - Share files to discuss - [info] 🌐
- KeysBand - Multi-key signing [source] 🌐
Code
- Stacks - AI Templates [info] [source] 🌐
- Nostrify - Share Nostr Frameworks 🌐
- Git Workshop (github like) [experimental] 🌐
- Gitstr (github like) [on development] ⏱️
- Osty [on development] [info] 🌐
- Python Nostr - Python Library for Nostr
- Sybil - Creating, managing and test Nostr events [on development] ⏱️
Relay Check and Cloud
- Nostr Watch - See your relay speed 🌐
- NosDrive - Nostr Relay that saves to Google Drive
Bidges and Getways
- Matrixtr Bridge - Between Matrix & Nostr
- Mostr - Between Nostr & Fediverse
- Nostrss - RSS to Nostr
- Rsslay - Optimized RSS to Nostr [source]
- Atomstr - RSS/Atom to Nostr [source]
Useful Profiles and Trends
nostr-voice - Voice note (just some clients)
NOT RELATED TO NOSTR
Voca - Text-to-Speech App for GrapheneOS [source] 🤖(on zapstore)
Android Keyboards
Personal notes and texts
Front-ends
- Nitter - Twitter / X without your data [source]
- NewPipe - Youtube, Peertube and others, without account & your data [source] 🤖
- Piped - Youtube web without you data [source] 🌐
Other Services
- Brave - Browser [source]
- DuckDuckGo - Search [source]
- LLMA - Meta - Meta open source AI [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Proton Mail - Mail [source]
Other open source index: Degoogled Apps
Some other Nostr index on:
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 0c65eba8:4a08ef9a
2025-05-24 15:09:03
@ 0c65eba8:4a08ef9a
2025-05-24 15:09:03Why This Matters and Why You're Worth It
You are not here by accident. You are here because a part of you knows you were meant for something more. Not just fleeting romance. Not just swipes, dates, and dead ends. But real, enduring marriages rooted in strength, beauty, reciprocity, and trust. One that leads to family, legacy, and love that doesn’t dissolve with time but deepens.
And yet, you’re being asked to do something that most women in history were never asked to do: choose your husband alone. That’s an incredible opportunity, but also a staggering risk. Choose well, and you build a joyful, secure life. Choose poorly, and the consequences can be devastating: emotional abuse, financial collapse, custody battles, long-term loneliness, or worse, a family without protection.
For centuries, women were guided. Communities, elders, and traditions helped narrow the field. Your tribe protected you. Your father filtered. Your aunties advised. They knew that mating is not merely emotional, it is economic, genetic, spiritual, and civilizational.
Today, most of those supports are gone. So now you must become the tribe. You must take responsibility for choosing wisely, and you must prepare yourself to be chosen by a man of wisdom, strength, and vision.
That’s why what follows is not emotional. It’s not romantic. It’s not easy. It is logical, operational, even harsh at times. Because lasting romance is earned by discipline. Because the real joy comes after the good decision is made. This document is your map, not to perfection, but to readiness.
This isn’t just about finding happiness. It’s about avoiding destruction. I’ve coached women for decades. I’ve seen the radiant peace of women who chose well, and the lifelong regret of those who didn’t. This isn’t theory. This is battlefield-tested. You may not like everything you read, but if you ignore it, you risk everything.
If you feel resistance, offense, or shame as you read, pause. That’s your signal. It’s not an attack. It’s a mirror. Let it reveal what still needs work. Avoid the temptation to point at men. This isn’t about men. This is about you. What you can control. What you can correct. What you can become.
Marriage is not a reward for love. It is a role. Wife. Mother. These are roles of the highest stakes, and therefore the highest standards. Standards you are capable of meeting.
This guide is written with love, not judgment. With concern, not control. It’s what every wise advisor, mentor, or coach who’s helped women into happy marriages would tell you. You’re not alone. But you are responsible.
Read with humility. Audit with courage. Plan with clarity. Change with resolve.
Natural Law Audit and Prescriptive Protocol for Female Readiness for Marriage-Intentional Courtship
Premise: From first principles of evolutionary necessity, behavioral causality, and the operational grammar of reciprocity, readiness for courtship with the intent of long-term pair bonding (marriage) is a function of a woman’s demonstrated ability to perform, signal, and sustain reciprocal value exchange over the duration of the male provisioning cycle. Courtship is a pre-contractual test of such capacity. This document synthesizes an evaluative and prescriptive audit for determining and restoring such readiness.
Meta-Readiness Considerations
I. Life Outcome Clarity and Expectation Calibration
Premise: A woman must understand what outcomes she genuinely seeks from life, maternal, relational, vocational, spiritual, or aesthetic, before selecting a mate. Courtship is a selection process for shared long-term production.
Natural Law Insight: Female wants are expansive and intertemporally unstable. Realism in selecting a partner requires narrowing aspirations to those outcomes reciprocally supportable by a male’s provisioning capacity. Misalignment between life design and mate capability produces disillusionment and conflict.
Recommendations:
-
Conduct a “Life Outcome Audit” to articulate non-negotiables vs. preferences.
-
Match aspirations (children, homemaking, lifestyle, location, work-life balance) to realistic provisioning tiers.
-
Recognize that hyperagency (excessive standards) without equivalent demonstrated value violates reciprocity.
-
Document target lifestyle and review against potential partner’s trajectory during vetting.
Conclusion: Selection must follow vision. A woman who does not know what she wants cannot choose a man who can build it with her.
II. Embedding in Normative Male-Led Communities
Premise: Participating in a structured, ethically-aligned male-led social network dramatically reduces pair-bonding risk and increases quality of mate options.
Natural Law Insight: Communities that enforce sexual modesty, honor reputation, and reward prosocial male leadership mirror Natural Law principles, even if expressed culturally or religiously. These environments serve as distributed vetting and enforcement systems.
Recommendations:
-
Seek participation in conservative religious congregations, traditional civic groups, or equivalent.
-
Avoid transient, libertine, or hyper-individualist networks that degrade accountability.
-
Use community gatekeepers as filters, eligible men will be known, observed, and reputation-bound.
-
Treat integration in such a network as a protective feature and quality signal, not a limitation.
Conclusion: Community is a vector of protection and opportunity. Women embedded in moral-order networks access both higher quality males and functional support for long-term bonding.
I. PHYSICAL FITNESS AND PRESENTATION
Functional Purpose: A woman’s physical presentation is not merely aesthetic, it is informational. It signals fertility, vitality, health, discipline, and self-respect. These traits are instinctively interpreted by men as indicators of long-term reproductive potential and cooperative stability. Sustained male interest begins with visible cues of youth and wellness, but is maintained by consistency in feminine self-maintenance. Being attractive is not about glamour; it is about broadcasting readiness for life partnership.
Operational Criteria:
-
Body Composition: WHR 0.7 ± 0.05, BMI 18.5–24.9.
-
Grooming: Routine hygiene, maintained hair, nails, skin.
-
Attire: Modest-congruent, form-accentuating without provocation.
-
Posture: Upright, balanced gait, open body language.
-
Non-Verbal Signaling: Frequent smiling, consistent eye contact.
Disqualifiers:
- Obesity, slovenliness, odor, posture collapse, erratic non-verbal cues.
Disqualifier Correction Protocol:
-
Minimum Standard: Restore BMI and WHR to target range, posture correction, grooming compliance.
-
Action Steps:
-
Daily calorie-controlled nutrition plan (90–120 days to compliance).
-
4x/week resistance/postural training.
-
Monthly wardrobe and grooming audit.
-
Mirror practice of expressiveness and gait.
Distinction: Short-term aesthetic changes do not replace sustained behavioral fitness.
II. PSYCHOLOGICAL MATURITY AND EMOTIONAL REGULATION
Functional Purpose: Emotional stability is not optional for pair bonding, it is foundational. A woman who cannot manage her internal state reliably becomes a source of constant stress for her partner, degrading his ability to provide, protect, and lead. Men bond most deeply with women who are consistent, safe, and affirming, not volatile or draining. Maturity means knowing how to pause, self-regulate, and respond thoughtfully rather than impulsively.
Operational Criteria:
-
Self-awareness, stable mood regulation, behavioral consistency.
-
Absence of excessive neuroticism, emotional impulsivity, passive aggression.
Disqualifiers:
- Excessive neuroticism, emotional impulsivity, public displays of instability, passive aggression.
Disqualifier Correction Protocol:
-
Minimum Standard: Self-narrative coherence, routine maintenance, calm conflict responses.
-
Action Steps:
-
30-day emotional trigger journaling.
-
Daily stoic self-inquiry and reframing.
-
90-day blackout on reactive digital communication.
-
Implement and maintain consistent wake/sleep rituals.
-
Avoid all stimulants.
Distinction: Restraint under pressure must be structural, not performative.
III. COGNITIVE AND COMMUNICATION SKILLS
Functional Purpose: Communication is the method by which needs, boundaries, plans, and responsibilities are negotiated in a family. A woman must be able to communicate her emotional and logistical realities without blame, manipulation, or avoidance. Equally, she must interpret and respect male communication styles and incentives. High-agency men require cooperative, reasoned conversation, not passive-aggressive signaling or emotional coercion.
Operational Criteria:
-
Rational dialogue, introspective clarity, emotional literacy.
-
Absence of GSRRM (Gossip, Shaming, Ridicule, Rallying, Moralizing).
Disqualifiers:
- Use of GSRRM tactics (Gossip, Shaming, Ridicule, Rallying, Moralizing), evasion, blame-shifting.
Disqualifier Correction Protocol:
-
Minimum Standard: Reasoned expression of internal states; dialectical discipline.
-
Action Steps:
-
Daily dialectic journaling (4-week review).
-
Replace projection/blame with inquiry scripting.
-
Weekly event narrative with personal responsibility.
-
Quarterly communication training.
-
Read Become Immune to Manipulation: How They Are Manipulating You (And How to Resist It) by Noah Revoy.
Distinction: Pleasantry and silence differ from communicative reciprocity.
IV. SOCIAL AND COOPERATIVE COMPETENCE
Functional Purpose: Marriage is not an isolated bond, it is embedded in a broader network of families, communities, and social systems. A woman must be able to adapt fluidly to cooperative roles, shifting from girlfriend to wife to mother without resisting the demands of each. Her ability to function harmoniously in social settings, defer to appropriate leadership, and support group cohesion is a strong indicator of her long-term fitness.
Operational Criteria:
-
Conflict de-escalation, status modesty, role fluidity.
-
Absence of contempt, manipulation, sabotage.
Disqualifiers:
- Misapplied contempt (directed at good-faith men or authority), sabotage of cooperative efforts, status-seeking via sexual leverage, or acts of public emasculation.
Disqualifier Correction Protocol:
-
Minimum Standard: Predictable, low-disruption group participation.
-
Action Steps:
-
Weekly feedback log on public interactions.
-
Acts of service in mixed-gender settings.
-
Non-romantic emulation of maternal/wifely behaviors.
-
Quarterly behavioral reviews with mentors or peers.
Distinction: Performative compliance without habituation is void.
V. DOMESTIC, ECONOMIC, AND LIFE-MANAGEMENT SKILLS
Functional Purpose: A stable household requires competence. Budgeting, scheduling, nutrition, and conflict resolution are not luxuries, they are the minimum viable functions of adult partnership. A woman who cannot manage herself will become a burden rather than a support. Readiness for marriage begins with self-sufficiency and extends into shared efficiency.
Operational Criteria:
-
Budgeting, scheduling, self-care, dietary planning.
-
Absence of chaos, compulsive consumption, disorganization.
Disqualifiers:
- Disorganized space, calendar chaos, debt, compulsive shopping, food delivery dependency.
Disqualifier Correction Protocol:
-
Minimum Standard: Domestic order, fiscal responsibility, time-discipline.
-
Action Steps:
-
30-day meal planning and budget logging.
-
Daily scheduling log with deviation analysis.
-
Audit digital purchases and reduce reliance on delivery.
-
14-day abstention from sugar, caffeine.
Distinction: Delegation without demonstrated competence is invalid.
VI. ATTITUDES AND WORLDVIEW ALIGNMENT
Functional Purpose: Every relationship is governed by implicit contracts. A woman’s worldview, what she believes about men, family, and authority, determines how she will perform in a marriage. If she views cooperation as oppression or expects benefits without contribution, she will destroy rather than build. Internal alignment with reciprocal duty and family structure is a non-negotiable foundation.
Operational Criteria:
-
Anti-entitlement, feminine aspiration, hierarchical acceptance.
-
Absence of adversarial ideology or egalitarian contractarianism.
Disqualifiers:
- Egalitarian contractarianism, careerism as identity, adversarial gender worldview.
Disqualifier Correction Protocol:
-
Minimum Standard: Adoption of reciprocal family economy worldview.
-
Action Steps:
-
Weekly entitlement vs obligation journaling.
-
Daily voluntary submission (non-critical contexts).
-
Narrative scripting using duty-driven framing.
-
Filter digital input to remove adversarial gender content.
Distinction: Ideological mimicry does not equal behavioral conversion.
VII. RISK PROFILE AND PAST BEHAVIOR
Functional Purpose: Past behavior is the strongest predictor of future conduct. A woman’s sexual, relational, and reputational history provides data on her loyalty, judgment, and risk to a man’s legacy. Men who are serious about marriage must screen for long-term predictability, not just short-term chemistry. Women who ignore their own histories are not protecting their futures.
Operational Criteria:
-
Modest sexual history, loyalty trend, third-party validation.
-
Absence of casual sex, serial monogamy, public instability.
Disqualifiers:
- History of casual sex, serial monogamy, divorce, paternity ambiguity, public drama.
Disqualifier Correction Protocol:
-
Minimum Standard: Transparent discontinuity with past disqualifiers.
-
Action Steps:
-
Public accounting of relationship past with responsibility acceptance.
-
Minimum 12-month monogamy/celibacy with logs.
-
Elimination of overt sexual signaling across all platforms.
-
Third-party testimonial verification.
Distinction: Claims of transformation without time-bound behavior are void.
Phased Rehabilitation Timeline for Readiness Restoration
Phase 1: Stabilization (Months 1–3)
-
Priority: Risk profile correction, emotional regulation, lifestyle order.
-
Focus: Sexual abstinence, emotional journaling, sleep/nutrition discipline.
Phase 2: Skill-Building (Months 4–6)
-
Priority: Domestic, communicative, and cognitive skills.
-
Focus: Meal budgeting, dialectical journaling, social role practice.
Phase 3: Social Re-Integration (Months 7–9)
-
Priority: Cooperative group behavior and worldview realignment.
-
Focus: Status modesty, deference rituals, ideological detox.
Phase 4: Courtship Re-Entry (Months 10–12)
-
Priority: Testifiability under male scrutiny, courtship conduct.
-
Focus: Third-party vetting system, courtship standards, mate discernment.
VIII. COURTSHIP ENTRY AND MALE VETTING PROTOCOL
Functional Purpose: The purpose of structured courtship and male vetting is to shift mate selection from emotionally reactive behavior to long-term rational strategy. Most modern women are tasked with a role their ancestors never bore alone: selecting a lifelong partner without the protective oversight of tribe, father, or community. This exposes them to profound risk, emotional, financial, sexual, and familial. Vetting is not a lack of faith in love, it is the discipline that makes real love sustainable.
By externalizing judgment to trusted men or professionals, a woman guards herself against the distortions of courtship neurochemistry (oxytocin, dopamine) and social pressure. More importantly, it signals to high-quality men that she values her future family enough to be discerning, and that she respects male judgment and leadership. Just as no wise man commits to a woman without proof of her virtue, no wise woman should commit to a man without proof of his character, stability, and alignment.
Vetting protects not only her body and emotions, but her legacy, and the children who will bear its consequences.
Operational Requirements:
-
Demonstrated sobriety from hormonal and emotional bias.
-
Third-party male oversight in mate evaluation.
Action Steps:
-
Triadic Vetting Structure: Enlist a minimum of two elder males (father, uncle, mentor) who:
-
Are happily married 10+ years.
-
Possess demonstrated judgment and ethical stability.
-
Have no romantic or competitive incentive to deceive.
-
Professional Support: If elder males are unavailable, retain a professional (licensed counselor, coach) with contractual duty of candor and no financial conflict of interest.
-
Vetting Sessions: All prospective partners undergo:
-
Disclosure-based interviews with vetting males.
-
Verification of sexual, financial, legal, and familial history.
-
Compatibility interrogation (religion, children, discipline, division of labor).
-
Hormonal Delay Protocol: Minimum 60-day abstention from physical intimacy until vetting phase is complete.
-
Documented Criteria: Maintain a checklist of reciprocal standards the male must meet (providing ability, decision-making, loyalty pattern, worldview alignment).
Rationale: Women under the influence of courtship neurochemicals (oxytocin, dopamine, serotonin) are neurologically biased toward over-valuation of male partners. This distortion is adaptive post-bonding but maladaptive pre-selection. Vetting externalizes judgment to disinterested, higher-agency observers.
Note for Both Sexes:
While this document serves women, the male counterpart should be studied concurrently. Understanding reciprocal obligations fosters selection integrity and eliminates false expectations. No woman should expect to secure a high-agency male without mirroring his investment in functional excellence, and vice versa.
Conclusion to Audit:
Readiness for marriage is a matter of demonstrated, reciprocal, operational fitness—not sentiment, rhetoric, or intention. This audit functions as both diagnostic and prescriptive framework. Each category of deficiency includes explicit steps for behavioral restitution. The phased timeline and courtship protocol ensure that no woman attempts entry into high-agency courtship without functional repair and reciprocal discernment. A woman prepared for marriage does not merely seek to be chosen; she earns rational preference by manifesting continuous, falsifiable, reciprocal value.
Final Word: You've Got This
You made it. That alone sets you apart. Most never read past the first page of what challenges them.
Now what?
If you identified areas where you fall short, good. That means the audit is working. Don’t stop there. Make a plan. Tackle one area at a time. Track progress. Be honest. Be relentless. And if you get stuck, ask. Ask someone older. Someone stable. Someone who has walked this path. Ask a happily married woman with children. Or invest in a professional who can guide you.
You were not meant to do this alone, but you are responsible for doing it honestly.
This path is hard. But so is being alone. So is pretending. So is chasing dreams built on fantasy instead of reality.
The woman who builds herself is the woman who builds a family. And the woman who builds a family, builds a civilization.
You’re not just choosing a man. You’re choosing a future.
Make it one worth living.
Common Objections, Honest Answers
“I don’t know any men worth putting that much effort in for.” That’s not because they don’t exist, it’s because the kind of man you’re looking for doesn’t advertise himself in chaos. High-value men are selective. They move in ordered circles, and they protect what they’ve built from anyone who might destabilize it. You won’t find them until you’ve become the kind of woman who belongs in that world.
“I don’t match several of these criteria and I still get plenty of attention from men.” There’s a difference between attention and intention. If you were attracting men who want to marry you, you’d be married. Being desired for casual access is not a sign of value, it’s often a sign of availability. Learn to tell the difference.
“Real men shouldn’t care about looks or checklists like this.” Real men care about what your appearance and habits say about your discipline, health, and self-respect. They’re not looking for shallow beauty, they’re looking for signs of stability and readiness. Being attractive is not about cosmetics. It’s about coherence. If you expect a man to invest everything in you, it’s fair that he checks the foundation.
“It’s judgmental, misogynistic, or unkind to talk about women like this.” Judging is what humans do. You’re judging this article right now. We all judge, because judgment is how we protect ourselves. Men who don’t know you can’t love you yet, they must judge first. Once they trust you, then love grows. This isn’t cruelty. It’s the path to safety.
“This is the most autistic, robotic thing I’ve ever read.” It might feel clinical. But the problems it addresses are deadly serious. Your feelings matter, but they won’t save your future. Logic is here to protect what feelings often ruin. There’s room for emotion, after the right foundation is laid.
“No man puts this much effort into judging women.” Some don’t. But you don’t want those men. Low-effort men are often desperate, flawed, or hiding their own disqualifiers. The kind of man who has the strength to say ‘no’ to a woman is the same man who can say ‘yes’ with purpose, and keep his promise.
“Shouldn’t love be unconditional?” Love isn’t based on your mood swings, but it is based on your virtue. We fall in love with the goodness in people, not just their personalities. Character inspires devotion. The stronger your character, the stronger and more lasting the love you will inspire.
“If I don’t want to change, shouldn’t someone love me as I am?” They might, but will they stay? You can love someone and still walk away if the cost is too high. Change isn’t about earning love, it’s about keeping it. Becoming better for yourself is the first act of love. Everything else flows from that.
“Why should I change just to get a man?” You shouldn’t. You should change to become your best self, healthier, stronger, more peaceful. That version of you will not only attract the right man, but she’ll enjoy her life more. Becoming marriageable is a side effect of becoming excellent. Do it for you. The right man will just be the reward.
-
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Problemas com Russell Kirk
A idéia central da “política da prudência[^1]” de Russell Kirk me parece muito correta, embora tenha sido melhor formulada pior no seu enorme livro do que em uma pequena frase do joanadarquista Lucas Souza: “o conservadorismo é importante, porque tem muita gente com idéia errada por aí, e nós podemos não saber distingüi-las”.
Porém, há alguns problemas que precisam ser esclarecidos, ou melhor explicados, e que me impedem de enxergar os seus argumentos como refutação final do meu já tão humilde (embora feroz) anarquismo. São eles:
I Percebo alguma coisa errada, não sei bem onde, entre a afirmação de que toda ideologia é ruim, ou “todas as ideologias causam confusão[^2]”, e a proposta conservadora de “conservar o mundo da ordem que herdamos, ainda que em estado imperfeito, de nossos ancestrais[^3]”. Ora, sem precisar cair em exemplos como o do partido conservador inglês -- que conservava a política inglesa sempre onde estava, e se alternava no governo com o partido trabalhista, que a levava cada vez mais um pouco à esquerda --, está embutida nessa frase, talvez, a idéia, que ao mesmo tempo é clara e ferrenhamente combatida pelos próprios conservadores, de que a história é da humanidade é uma história de progresso linear rumo a uma situação melhor.
Querer conservar o mundo da ordem que herdamos significa conservar também os vários erros que podem ter sido cometidos pelos nossos ancestrais mais recentes, e conservá-los mesmo assim, acusando toda e qualquer tentativa de propôr soluções a esses erros de ideologia? Ou será que conservar o mundo da ordem é escolher um período determinado que seja tido como o auge da história humana e tentar restaurá-lo em nosso próprio tempo? Não seria isto ideologia?
Ou, ainda, será que conservar o mundo da ordem é selecionar, entre vários períodos do passado, alguns pedaços que o conservador considerar ótimos em cada sociedade, fazer dali uma mistura de sociedade ideal baseada no passado e então tentar implementá-la? Quem saberia dizer quais são as partes certas?
II Sobre a questão do que mantém a sociedade civil coesa, Russell Kirk, opondo-a à posição libertária de que o nexo da sociedade é o autointeresse, declara que a posição conservadora é a de que “a sociedade é uma comunidade de almas, que une os mortos, os vivos e os ainda não nascidos, e que se harmoniza por aquilo que Aristóteles chamou de amizade e os cristãos chamam de caridade ou amor ao próximo”.
Esta é uma posição muito correta, mas me parece estar em contradição com a defesa do Estado que ele faz na mesma página e na seguinte. O que me parece errado é que a sociedade não pode ser, ao mesmo tempo, uma “comunidade baseada no amor ao próximo” e uma comunidade que “requer não somente que as paixões dos indivíduos sejam subjugadas, mas que, mesmo no povo e no corpo social, bem como nos indivíduos, as inclinações dos homens, amiúde, devam ser frustradas, a vontade controlada e as paixões subjugadas” e, pior, que “isso somente pode ser feito por um poder exterior”.
Disto aí podemos tirar que, da mesma forma que Kirk define a posição libertária como sendo a de que o autointeresse é que mantém a sociedade civil coesa, a posição conservadora seria então a de que essa coesão vem apenas do Estado, e não de qualquer ligação entre vivos e mortos, ou do amor ao próximo. Já que, sem o Estado, diz, ele, citando Thomas Hobbes, a condição do homem é “solitária, pobre, sórdida, embrutecida e curta”?
[^1]: este é o nome do livro e também um outro nome que ele dá para o próprio conservadorismo (p.99). [^2]: p. 101 [^3]: p. 102
-
 @ 3f770d65:7a745b24
2024-06-17 18:56:54
@ 3f770d65:7a745b24
2024-06-17 18:56:54Several months ago, nostr:npub1hqaz3dlyuhfqhktqchawke39l92jj9nt30dsgh2zvd9z7dv3j3gqpkt56s and I set out to do tackle a task that had never been done before throughout Nostr's short history. We decided adopt the "go big, or go home" mentality and give our best effort to Purple Pill all of the nostr:npub167n5w6cj2wseqtmk26zllc7n28uv9c4vw28k2kht206vnghe5a7stgzu3r conference.
We couldn't accomplish this monumental task without the help of the Nostr community. From every day Nostriches and plebs, to legendary developers putting their blood, sweat, and tears into building this new protocol, to several companies within the Nostr ecosystem, everyone was going to need to do their part to turn this dream into a reality.
The mission
For the original vision of Nostr at BTC Prague, we planned on supporting the smallest available booth and a small panel on the secondary stage. The plan was for any Nostr developer to contribute what they could and then use the Nostr booth as a central hub to onboard users to their applications, provide support to their users, and meet the community. I embarked on my first crowdfunding journey and was able to initially raise over 10M sats thanks to the greater Nostr community donating towards our efforts.
Shortly afterwards, I was approached by nostr:npub1dtgg8yk3h23ldlm6jsy79tz723p4sun9mz62tqwxqe7c363szkzqm8up6m from Satlantis. He had planned on doing a mainstage presentation at BTC Prague on his new Nostr powered application. He asked me if I wanted to combine our efforts to upgrade the Nostr booth to the largest booth possible to give Nostr an even larger presence. I reached out to Avi and several other trusted Nostriches to see their opinions on this potential upgrade and everyone seemed to agree that we should continue with the "go big, or go home" mentality and try our best to Purple Pill all of Prague.
Now with a larger goal at hand, we were able to garner even more support from the Nostr community in addition by adding Highlighter from nostr:npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft and Primal from nostr:npub16c0nh3dnadzqpm76uctf5hqhe2lny344zsmpm6feee9p5rdxaa9q586nvr as larger contributors.
The final tallies for funds raised were 16M+ sats from the greater Nostr community and 38M+ sats raised from Satlantis, Primal, and Highlighter. (We did have to raise a little more than originally anticipated because the Bitcoin 58K Gang made the fiat value of Bitcoin dip down for a bit right when we were trying to finalize payment.)
Putting it all together
This support enabled us to secure one of the four large booths at BTC Prague and a main stage panel. Given that these three companies made significant contributions, enabling our acquisition of the largest booth, we decided that it was logical to feature these companies more prominently. However, it was crucial to strike a delicate balance here. While emphasizing that this booth represented the Nostr community and was a true community effort, we also wanted to acknowledge and showcase those who made it possible. These companies could have opted for smaller individual booths, but their collaboration in a unified space demonstrates Nostr's principles of openness and interoperability—demonstrating that everyone and everything can work together seamlessly.
Therefore, we included as many logos across the Nostr ecosystem as possible throughout our iconography.

And, we also had a dedicated area of the booth highlighting our larger contributors.

The results exceeded all expectations. For three days during the BTC Prague conference, the Nostr booth was continuously bustling with activity. Attendees ranged from individuals who had never heard of Nostr before to those who were curious, active users within the ecosystem, and developers creating the applications we use daily. It was a remarkable community effort, with unexpected volunteers stepping up to onboard new users and provide support. Recognizing our busy schedules and flocks of new Nostriches hatching, they chose to assist in our efforts, offering help, and answering questions. It was a truly inspiring experience. Despite the busyness, the enthusiasm and support of so many people made each day enjoyable and dynamic, ensuring there was never a dull moment and we were always surrounded by friends.
Booth takeaways
As this was our very first attempt at doing something like this, I'd like to do a personal post mortem and highlight many of our successes and even some areas where I feel we can improve upon in the future.
Several Nostriches went above and beyond, helping onboard people and answer questions for three days straight. nostr:npub17plqkxhsv66g8quxxc9p5t9mxazzn20m426exqnl8lxnh5a4cdns7jezx0 nostr:npub1spdnfacgsd7lk0nlqkq443tkq4jx9z6c6ksvaquuewmw7d3qltpslcq6j7 nostr:npub1v0lxxxxutpvrelsksy8cdhgfux9l6a42hsj2qzquu2zk7vc9qnkszrqj49 nostr:npub1k6tqlj78cpznd0yc74wy3k0elmj4nql87a3uzfz98tmj3tuzxywsf0dhk6 nostr:npub1md39ua3h2s7204a7v5p9sdxmxx9qc7m4kr3r6naeuwfznad6d7nsxpctp9 nostr:npub1arkn0xxxll4llgy9qxkrncn3vc4l69s0dz8ef3zadykcwe7ax3dqrrh43w nostr:npub1zga04e73s7ard4kaektaha9vckdwll3y8auztyhl3uj764ua7vrqc7ppvc were the lifeblood of the booth, always answering questions themselves or referring them to others if they were unable to help, didn't know the answer or were busy at the time. You all put in the work and deserve much credit and thanks. Even nostr:npub1995y964wmxl94crx3ksfley24szjr390skdd237ex9z7ttp5c9lqld8vtf was helping with onboarding!

Additionally, beyond general use case questions, we also had many developers stop by and answer many more technical questions for those wanting to learn a bit more too. nostr:npub1zach44xjpc4yyhx6pgse2cj2pf98838kja03dv2e8ly8lfr094vqvm5dy5 nostr:npub1v0lxxxxutpvrelsksy8cdhgfux9l6a42hsj2qzquu2zk7vc9qnkszrqj49 nostr:npub1arkn0xxxll4llgy9qxkrncn3vc4l69s0dz8ef3zadykcwe7ax3dqrrh43w nostr:npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft were often seen answering more technical questions on various developmental topics.


Identifying areas for improvement is challenging, as the entire team of Nostriches performed exceptionally well, exceeding expectations. The event was a whirlwind of activity, with constant engagement and zero downtime. Volunteers seamlessly rotated at the front counter answering questions and distributing items to attendees. (Thanks nostr:npub1cgcwm56v5hyrrzl5ty4vq4kdud63n5u4czgycdl2r3jshzk55ufqe52ndy . Your nostr.how and nostrapps.com business cards were a HUGE help here!)
Full disclosure, I personally didn't leave the booth for three days all that much for two reasons. 1) Because I love to #GrowNostr and talk to people and 2) Because I was worried that the booth would turn into a corporate Primal or Satlantis show. However, this wasn't the case. While these teams did have a large presence with many team members all wearing t-shirts, none of my fears became a reality. If people asked questions about Nostr in general, that was discussed. If people asked questions about Primal or Satlantis, that was discussed. I personally recommended numerous social apps, Damus, Amethyst, Primal, Nostur, Nos.social - all of them. The booth was a true decentralized effort and I absolutely did not need to worry as much as I did, but I felt like I had an obligation to fulfill and I wanted to be there to see it through.
If I had to choose an area that needed improvement, I'd say that the three Satlantis women that nostr:npub1dtgg8yk3h23ldlm6jsy79tz723p4sun9mz62tqwxqe7c363szkzqm8up6m brought with him were supposed to shadow some of us to learn more about Nostr, so that they could then use this information to do the initial intake booth questions before making the referral to those with more information, but this just didn't happen. We were all so busy. Sorry! It was just too hard to coordinate. Maybe in the future we can prepare a bit more in this area. Although, nostr:npub1hz5alqscpp8yjrvgsdp2n4ygkl8slvstrgvmjca7e45w6644ew7sewtysa did a fantastic job, jumping right in there head first!
Secondly, we could have improved our television capabilities. We rotated from showing the live dashboard from the booth's Zap.stream livestream, to showing Primal.net/explore Nostr statistics, to showing nostr:npub1lelkh3hhxw9hdwlcpk6q9t0xt9f7yze0y0nxazvzqjmre3p98x3sthkvyz 's Nostr Documentary on loop, to playing the Satlantis promotional video. The majority of the time our TV was playing the same Nostr Documentary. It's great! I love that video, but we may be able to work out a better schedule and rotation mechanism in the future to showcase more content equally. Plus, I don't want to always be on the TV. I don't want people getting the wrong idea.
Nostr takeaways
After speaking with hundreds of people at BTC Prague, I feel that I've discovered the best way to describe Nostr.
Nostr has a portable digital social identity, allowing you to be in control of your digital social identity for the very first time, allowing you to take your entire social graph with you, every time you use a different application from Nostr's ecosystem.
Nostr is the social glue that binds all of your apps together.
In general, at BTC Prague, while explaining Nostr to people, the digital social identity route was what clicked with the most people. From there, it's not a long stretch to understand building a reputation and web of trust either.
Many people do not use the "Other Stuff" and explaining to them how to use these applications is hard. People want a native application.
Damus, Primal, and Amethyst seem to be the number one apps that people are using, with maybe Primal being the number one altogether? This is probably due to Primal being available on Android, iOS, and the web. Also, many people don't know that Damus still supports Zaps via the Nostr script workaround. I had to show many how to enable Zaps.
Everyone wants Nostr at their conference
There is significant interest in featuring Nostr at various conferences. Although not everyone has reached out, numerous individuals at BTC Prague expressed enthusiasm about incorporating a Nostr booth, along with several Nostr talks and sessions, into their upcoming events. They recognize the critical role Nostr and free speech play globally and acknowledge Nostr's popularity within the Bitcoin community. However, they also understand that more work is needed, and we must continue our efforts to onboard and engage new users.

I have two primary observations on this matter:
-
The community effort demonstrated here serves as a blueprint for success. We have proven that this approach to growing Nostr is effective, desired, and necessary. The engagement at our booth and attendance at our panels prove this with ease.
-
This fundraising initiative is likely a one-time effort. I cannot, in good conscience, continue to ask the community to bootstrap these endeavors. If we are to sustain these booths and promote Nostr at similar conferences, the conference organizers themselves must provide substantial support or discounts to foster broader Nostr adoption. While I understand that conferences entail significant operational costs, it is not feasible for Nostr developers and the broader Nostr community to finance these efforts continuously. Additionally, I would not feel comfortable requesting financial contributions from you all again for this purpose.
Looking forward
Will we do _this _again? I don't know. While our initial endeavor was a complete success, it would be unfortunate to cease our efforts just as we are gaining momentum.
Avi and I have a lot to discuss between ourselves and a lot to discuss with all of you.
Thank you all from the bottom of my heart. Thank you nostr:npub1dtgg8yk3h23ldlm6jsy79tz723p4sun9mz62tqwxqe7c363szkzqm8up6m nostr:npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft nostr:npub16c0nh3dnadzqpm76uctf5hqhe2lny344zsmpm6feee9p5rdxaa9q586nvr for making all of this possible. Thank you to every single Nostrich that donated your hard earned sats to make this possible. Thank you to all of the developers that built all of this to make all of this possible. Thank you to everyone else <3
Keep building.
-
-
 @ 95cbd62b:a5270126
2025-05-23 10:12:48
@ 95cbd62b:a5270126
2025-05-23 10:12:48Nếu bạn đang tìm kiếm một nền tảng cá cược trực tuyến uy tín, hỗ trợ tiếng Việt toàn diện, tích hợp nhiều tính năng hiện đại và mang lại cơ hội kiếm thưởng mỗi ngày thì 123BET chính là lựa chọn hoàn hảo. Được xây dựng với định hướng lấy người dùng làm trung tâm, 123BET mang đến trải nghiệm cá cược tối ưu với giao diện đơn giản, dễ thao tác, tương thích tốt trên mọi thiết bị từ máy tính đến điện thoại. Người chơi chỉ cần đăng ký một tài khoản duy nhất là có thể truy cập toàn bộ hệ sinh thái giải trí khổng lồ bao gồm slot game, casino trực tuyến, game bắn cá, mini game dân gian và cá cược thể thao. Bên cạnh đó, 123BET còn chú trọng đến bảo mật bằng cách tích hợp các phương thức đăng nhập hiện đại như OTP, nhận diện khuôn mặt và vân tay. Ứng dụng di động 123BET App được tối ưu hóa để truy cập mượt mà không bị chặn, đồng thời hỗ trợ thông báo khuyến mãi tức thời giúp người chơi không bỏ lỡ bất kỳ ưu đãi nào.
Kho game của 123BET là một thế giới giải trí đầy màu sắc, được cung cấp bởi các nhà phát hành danh tiếng toàn cầu như PG Soft, JILI, Pragmatic Play, Microgaming và Spadegaming cho dòng slot game. Tại đây, người chơi có thể trải nghiệm hàng trăm chủ đề phong phú, từ cổ điển đến hiện đại, với các tính năng đặc biệt như vòng quay miễn phí, hệ số nhân, jackpot lũy tiến và các mini game bonus đầy hấp dẫn. Với những ai yêu thích không khí sòng bài thật, mảng casino trực tiếp của 123BET mang đến trải nghiệm chân thực với video phát sóng trực tiếp chất lượng cao từ các studio như SA Gaming, Evolution, WM Casino và Dream Gaming. Game bắn cá cũng là điểm nhấn không thể bỏ qua với hình ảnh 3D sắc nét, hiệu ứng đạn sinh động, nhiều chế độ chơi từ cá nhân đến tổ đội, vũ khí đa dạng và đặc biệt là khả năng đổi xu thành tiền thật nhanh chóng. Với hàng loạt trò chơi hấp dẫn như Monster Awaken, Fishing War hay Bombing Fishing, người chơi có thể vừa giải trí vừa gia tăng thu nhập mỗi ngày.
Không chỉ nổi bật về mặt nội dung, 123BET còn ghi điểm mạnh với hệ thống nạp – rút tự động 24/7, tốc độ xử lý nhanh, không giới hạn số lần giao dịch và hoàn toàn miễn phí. Người chơi có thể linh hoạt nạp tiền qua nhiều kênh như chuyển khoản ngân hàng nội địa, ví điện tử (Momo, ZaloPay, ViettelPay) hoặc QR Code chỉ trong vòng 1–3 phút. Quy trình rút tiền đơn giản, hỗ trợ về tài khoản ngân hàng chính chủ, đảm bảo tiền về nhanh chỉ sau 5–10 phút kể cả vào ban đêm hoặc ngày lễ. Ngoài ra, 123BET còn thường xuyên triển khai các chương trình khuyến mãi hấp dẫn như thưởng 100% nạp đầu, hoàn tiền hàng ngày cho tất cả trò chơi, ưu đãi nạp lại cuối tuần, tặng quà sinh nhật và nâng hạng VIP với đặc quyền riêng. Đặc biệt, người chơi có thể kiếm thêm thu nhập thụ động thông qua chương trình giới thiệu bạn bè nhận hoa hồng không giới hạn. Với đội ngũ hỗ trợ kỹ thuật chuyên nghiệp 24/7 và chính sách chăm sóc khách hàng tận tình, 123BET đang khẳng định vị thế hàng đầu trong lĩnh vực cá cược trực tuyến tại thị trường Việt Nam, mang đến một sân chơi an toàn, công bằng và sinh lợi bền vững cho tất cả người chơi.
-
 @ f6488c62:c929299d
2025-05-23 09:48:20
@ f6488c62:c929299d
2025-05-23 09:48:20ในวันที่ 23 พฤษภาคม 2568 The Wall Street Journal รายงานข่าวที่น่าสนใจว่า ธนาคารยักษ์ใหญ่ของสหรัฐฯ เช่น JPMorgan Chase, Bank of America, Citigroup และ Wells Fargo กำลังพิจารณาความเป็นไปได้ในการพัฒนา Stablecoin ร่วมกัน เพื่อก้าวเข้าสู่โลกของคริปโตเคอเรนซีอย่างเต็มตัว การเคลื่อนไหวครั้งนี้ไม่เพียงสะท้อนถึงการยอมรับสินทรัพย์ดิจิทัลในระบบการเงินกระแสหลัก แต่ยังเป็นก้าวสำคัญในการรักษาความเป็นผู้นำของเงินดอลลาร์สหรัฐในยุคการเงินดิจิทัล.
Stablecoin: อนาคตของการชำระเงินดิจิทัล Stablecoin เป็นสกุลเงินดิจิทัลที่ออกแบบมาเพื่อลดความผันผวนโดยผูกมูลค่ากับสินทรัพย์ที่มีเสถียรภาพ เช่น เงินดอลลาร์สหรัฐ ทำให้เหมาะสำหรับการใช้ในระบบการชำระเงิน การโอนเงินข้ามพรมแดน และการเงินแบบกระจายศูนย์ (DeFi). การที่ธนาคารใหญ่ของสหรัฐฯ หันมาสนใจ Stablecoin ร่วมกัน แสดงถึงความพยายามในการปรับตัวให้เข้ากับความต้องการของผู้บริโภคยุคใหม่ที่ต้องการความรวดเร็วและประหยัดต้นทุนในการทำธุรกรรมทางการเงิน.
ทำไมธนาคารถึงสนใจ Stablecoin? ในปี 2568 ตลาดคริปโตเคอเรนซีกำลังร้อนแรง โดยมูลค่าตลาดรวมของคริปโตทั่วโลกอยู่ที่ 3.64 ล้านล้านดอลลาร์ ซึ่งในจำนวนนี้ Bitcoin มีมูลค่าตลาดสูงสุดที่ 2.2 ล้านล้านดอลลาร์ และราคา Bitcoin ล่าสุดพุ่งแตะ 111,160.66 ดอลลาร์ (ข้อมูล ณ วันที่ 23 พฤษภาคม 2568 เวลา 16:44 น. ตามเขตเวลา +07) นอกจากนี้ ยังมีเม็ดเงินไหลเข้าสู่กองทุนสินทรัพย์ดิจิทัลในสหรัฐฯ กว่า 7.5 พันล้านดอลลาร์ การที่ธนาคารยักษ์ใหญ่ที่มีมูลค่ารวมกันถึง 8 ล้านล้านดอลลาร์เข้ามาในสนามนี้ แสดงถึงศักยภาพในการเปลี่ยนแปลงภูมิทัศน์ของอุตสาหกรรมการเงิน. นโยบายที่เอื้ออำนวยต่อคริปโตในยุคของประธานาธิบดีโดนัลด์ ทรัมป์ และการลดดอกเบี้ยนโยบายของ Fed ยังเป็นปัจจัยสนับสนุนที่สำคัญ.
โอกาสและความท้าทาย การพัฒนา Stablecoin ร่วมกันของธนาคารเหล่านี้เปิดโอกาสให้สหรัฐฯ รักษาความเป็นผู้นำในระบบการเงินดิจิทัล และเพิ่มประสิทธิภาพในระบบการชำระเงินทั่วโลก อย่างไรก็ตาม ความท้าทายที่รออยู่คือการแข่งขันกับ Stablecoin ที่ครองตลาด เช่น USDT และ USDC รวมถึงความไม่แน่นอนด้านกฎระเบียบและความผันผวนของเศรษฐกิจโลกจากนโยบายการค้าของสหรัฐฯ. ธนาคารจะต้องลงทุนในโครงสร้างพื้นฐานที่ปลอดภัยและสอดคล้องกับกฎหมาย เพื่อสร้างความไว้วางใจจากผู้ใช้.
มองไปข้างหน้า การที่ธนาคารชั้นนำของสหรัฐฯ หันมาสนใจ Stablecoin เป็นสัญญาณที่ชัดเจนว่าโลกการเงินกำลังเปลี่ยนผ่านสู่ยุคดิจิทัลอย่างเต็มรูปแบบ การเคลื่อนไหวครั้งนี้อาจเป็นจุดเปลี่ยนที่ทำให้คริปโตเคอเรนซีกลายเป็นส่วนสำคัญของระบบการเงินกระแสหลัก อย่างไรก็ตาม ความสำเร็จจะขึ้นอยู่กับความสามารถในการสร้างนวัตกรรมที่ตอบโจทย์ผู้บริโภคและการจัดการกับความท้าทายด้านกฎระเบียบและการแข่งขันในตลาด. ในอนาคตอันใกล้ Stablecoin จากธนาคารยักษ์ใหญ่อาจกลายเป็นตัวเปลี่ยนเกมในวงการการเงินโลก และเป็นเครื่องมือสำคัญในการเชื่อมโยงระบบการเงินแบบดั้งเดิมเข้ากับโลกดิจิทัล นักลงทุนและผู้บริโภคควรจับตาดูความคืบหน้าของโครงการนี้อย่างใกล้ชิด เพราะมันอาจเป็นก้าวแรกสู่การปฏิวัติครั้งใหญ่ในวงการการเงิน.
-
 @ 2b24a1fa:17750f64
2025-05-22 19:44:28
@ 2b24a1fa:17750f64
2025-05-22 19:44:28„Triff niemals deine Idole“ heißt ein gängiger Ratschlag. In gewendeten Zeiten stehen zu dem die Werte auf dem Kopf – und manche Künstler mit ihnen. Die Worte, die aus manch ihrer Mündern kommen, wirken, als hätte eine fremde Hand sie auf deren Zunge gelegt.
https://soundcloud.com/radiomuenchen/wolf-biermann-und-sein-falscher-friede-von-alexa-rodrian?
Die Sängerin Alexa Rodrian erlebte bei der Verleihung des Deutschen Filmpreises einen solchen Moment der Desillusion. Es war der Auftritt des Liedermachers Wolf Biermann. Hören Sie hierzu Alexa Rodrians Text „Wolf Biermann und sein falscher Friede“.
Bild: Marco Maas/fotografirma.de
-
 @ 90c656ff:9383fd4e
2025-05-24 12:06:36
@ 90c656ff:9383fd4e
2025-05-24 12:06:36Throughout history, money has always been under the control of central authorities, such as governments and banks. These intermediaries have set the rules of the financial system, controlled the issuance of currency, and overseen transactions. However, with the emergence of Bitcoin, a new paradigm began to take shape: decentralized money. This transformation represents a profound shift in how people store and transfer value, challenging the traditional financial model.
- The traditional model: centralized money
01 - Dependence on intermediaries: To carry out transactions, people rely on banks, governments, and other regulatory entities.
02 - Inflation and devaluation: Central banks can print money endlessly, often leading to a loss in purchasing power.
03 - Censorship and restrictions: Access to money can be denied for political, bureaucratic, or institutional reasons, limiting individuals’ financial freedom.
Despite being the dominant model for centuries, the centralized system has shown its vulnerabilities through numerous economic and political crises. It was in this context that Bitcoin emerged as an innovative alternative.
- The revolution of decentralized money
01 - Elimination of intermediaries: Transactions can be made directly between users, without the need for banks or financial companies.
02 - Limited and predictable supply: Bitcoin has a fixed cap of 21 million units, preventing the inflation caused by excessive money printing.
03 - Censorship resistance: No entity can block or prevent transactions, ensuring full financial freedom.
04 - Self-custody: Each user can hold their own funds without relying on a bank or any other institution.
This paradigm shift has a significant impact not only on the financial system but also on how people interact with money and protect their wealth.
Challenges and opposition to financial decentralization
The transition to a decentralized financial system faces several challenges, the main one being resistance from traditional institutions. Banks and governments see Bitcoin as a threat to their control over money and seek to regulate or limit its adoption.
There are also technical and educational barriers. Many people still do not fully understand how Bitcoin works, which can hinder its adoption. However, as more people become aware of the benefits of decentralized money, its use is likely to grow.
In summary, the shift from a centralized financial system to a decentralized one represents one of the most significant transformations of the digital era. Bitcoin leads this movement by offering a censorship-resistant, transparent, and accessible alternative. Despite opposition from the traditional system, the decentralization of money continues to gain momentum, providing greater autonomy and financial freedom to people around the world. This revolution is not just technological, but also social and economic—redefining the way the world understands and uses money.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!