-
 @ b8851a06:9b120ba1
2025-01-19 22:05:55
@ b8851a06:9b120ba1
2025-01-19 22:05:55A TALE OF RESILIENCE
Nine years ago today, The Washington Post declared "R.I.P. Bitcoin" when the cryptocurrency traded at $380. Fast forward to January 19, 2025, and Bitcoin trades at $104,803, representing a staggering 27,500% increase since that infamous obituary.
The Numbers Tell the Story
🔘 Bitcoin has been declared dead 477 times since its inception
🔘 2023 saw only 8 death notices, a decade-low
🔘 2024 recorded just 2 death declarations, compared to 124 in 2017
From Mockery to Mainstream
The transformation has been remarkable. When the Washington Post published its obituary, Bitcoin was dismissed as a fringe technology. Today, it's embraced by financial giants like BlackRock and Fidelity. The price history tells an compelling story.
The Future Outlook
Despite past skepticism, institutional analysts now project ambitious targets. Galaxy Digital predicts Bitcoin could exceed $150,000 in the first half of 2025. This represents a dramatic shift from the days when Nobel laureates and banking executives routinely dismissed Bitcoin as worthless.
A Lesson in Resilience
The premature death notice serves as a powerful reminder about the dangers of dismissing innovative technologies. While Bitcoin faced numerous challenges since 2016, including regulatory crackdowns and market crashes, its fundamental value proposition has remained intact. The declining frequency of "Bitcoin obituaries" suggests that even its harshest critics are beginning to acknowledge its staying power.
There is no second best, and it’s going to millions.
-
 @ 7f29628d:e160cccc
2025-01-07 11:50:30
@ 7f29628d:e160cccc
2025-01-07 11:50:30Der gut informierte Bürger denkt bei der Pandemie sofort an Intensivstationen, an die Bilder aus Bergamo und erinnert sich an die Berichterstattung damals – also muss es wohl ein Maximum gewesen sein. Manche Skeptiker behaupten jedoch das Gegenteil. Klarheit sollte ein Blick nach Wiesbaden, zum Statistischen Bundesamt, schaffen. Schließlich sitzen dort gut bezahlte Profis, die seit vielen Jahrzehnten die Sterbestatistik pflegen und veröffentlichen. Jeder Todesfall wird in Deutschland über die Standesämter exakt erfasst.
Doch die Überraschung: Das Statistische Bundesamt liefert uns auf diese einfache Frage zwei extrem unterschiedliche Antworten – ein Minimum und ein Maximum. Das Ergebnis hängt davon ab, wie tief man in die Veröffentlichungen des Bundesamtes eintaucht. Betrachtet man nur die Webseiten und Pressemitteilungen, erhält man den Eindruck eines Maximums. Schaut man jedoch etwas tiefer in die Tabellen und Rohdaten, zeigt sich plötzlich ein Minimum. Aber wie kann das sein? Beides gleichzeitig geht ja wohl kaum. Wer lügt hier – die Tabellen des Amtes oder die Pressemitteilungen? Gehen wir dieser Frage Schritt für Schritt auf den Grund.
2020: Ein historisches Maximum?
Schauen wir uns die vielen Hundert Veröffentlichungen des Statistischen Bundesamtes aus dieser Zeit an. Oder wir kürzen ab und fragen ChatGPT, da die KI auf diesen Daten trainiert wurde und das gesamte Material kennt. Die Frage an ChatGPT lautet also: Wie war das Sterbegeschehen im Jahr 2020 im Vergleich zu den Vorjahren?
ChatGPT antwortet: »Im Jahr 2020 war die Sterblichkeit in Deutschland höher als in den Jahren zuvor. Es gab eine Übersterblichkeit von etwa 982.000 Todesfällen, das sind rund 46.000 mehr als der Durchschnitt der Vorjahre (2016 bis 2019). Dieser Anstieg wurde überwiegend im Zusammenhang mit der COVID-19-Pandemie gesehen. Während die Sterbezahlen in den Vorjahren schwankten, war ein solch signifikanter Anstieg wie 2020 bisher nicht zu beobachten.«
Wir fragen konkreter: Ist es ein Fakt, dass wir eine so ernste Lage im Sterbegeschehen wie im Frühjahr 2020 noch nie erlebt haben?
ChatGPT bestätigt: »Ja, die COVID-19-Pandemie führte im Frühjahr 2020 zu einer außergewöhnlichen Situation im Sterbegeschehen in Deutschland. Die dramatische Übersterblichkeit, die ab der 13. Kalenderwoche auftrat, veranlasste das Statistische Bundesamt, besonders eindringliche Warnungen zu veröffentlichen. Der damalige Vizepräsident des Amtes und andere führende Stimmen wiesen öffentlich darauf hin, dass die Todesfallzahlen stark vom Durchschnitt abwichen. Diese klare Warnung richtete sich an die Öffentlichkeit und die Politik gleichermaßen. Die Medien berichteten intensiv über diese Warnungen, was das Bewusstsein für die Schwere der Pandemie erheblich schärfte. In den vergangenen Jahrzehnten hatte es keine vergleichbare Übersterblichkeit gegeben, die eine solch umfangreiche Kommunikation durch das Statistische Bundesamt erforderlich gemacht hätte.«
Ein gut informierter Zeitungsleser wird sich an dieser Stelle bestätigt fühlen: Ja, so war es damals. Ein Maximum im Sterbegeschehen – wegen der Pandemie. Oder etwa nicht?
2020: Ein historisches Minimum?
Tauchen wir in die Rohdaten des Statistischen Bundesamtes ein. Die Tabellen, die das Amt seit Jahrzehnten verlässlich veröffentlicht, nennen sich Sterbetafeln. Diese werden jährlich bereitgestellt und stehen auf der Website des Bundesamtes zum Download bereit. Ein erster Blick in die Sterbetafeln mag den Laien abschrecken, doch mit einer kurzen Erklärung wird alles verständlich. Wir gehen schrittweise vor.
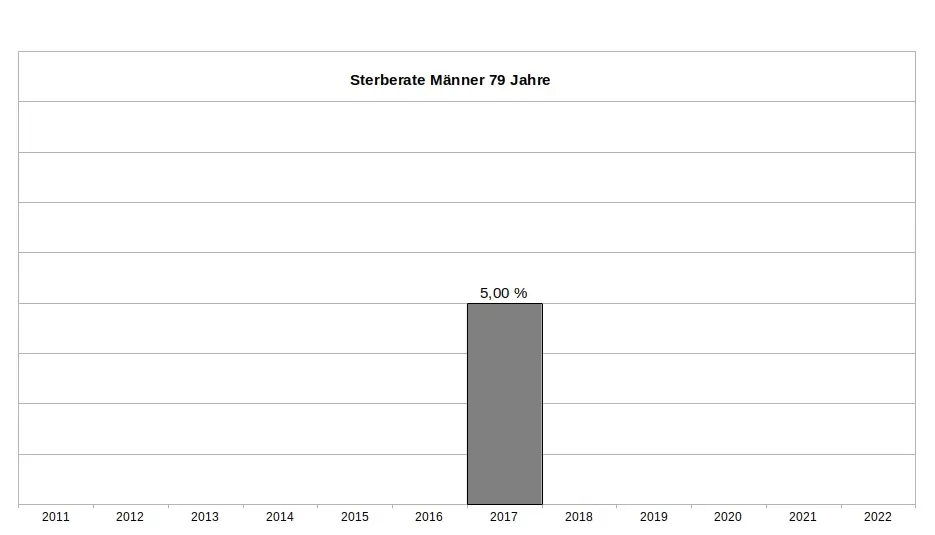
Nehmen wir die Sterbetafel des Jahres 2017. Sie enthält zwei große Tabellen – eine für Männer und eine für Frauen. Jede Zeile der Tabelle steht für einen Jahrgang, zum Beispiel zeigt die Zeile 79 die Daten der 79-jährigen Männer. Besonders wichtig ist nun die zweite Spalte, in der der Wert 0,05 eingetragen ist. Das bedeutet, dass 5 Prozent der 79-jährigen Männer im Jahr 2017 verstorben sind. Das ist die wichtige Kennzahl. Wenn wir diesen exakten Wert, den man auch als Sterberate bezeichnet, nun in ein Säulendiagramm eintragen, erhalten wir eine leicht verständliche visuelle Darstellung (Grafik 1).
Es ist wichtig zu betonen, dass dieser Wert weder ein Schätzwert noch eine Modellrechnung oder Prognose ist, sondern ein exakter Messwert, basierend auf einer zuverlässigen Zählung. Sterberaten (für die Fachleute auch Sterbewahrscheinlichkeiten qx) sind seit Johann Peter Süßmilch (1707–1767) der Goldstandard der Sterbestatistik. Jeder Aktuar wird das bestätigen. Fügen wir nun die Sterberaten der 79-jährigen Männer aus den Jahren davor und danach hinzu, um das Gesamtbild zu sehen (Grafik 2). Und nun die entscheidende Frage: Zeigt das Jahr 2020 ein Maximum oder ein Minimum?
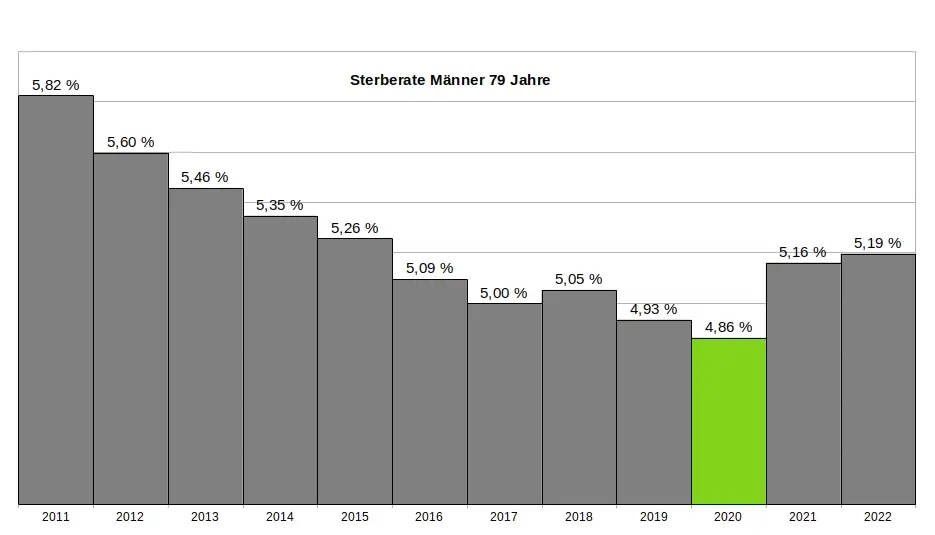
Ein kritischer Leser könnte vermuten, dass die 79-jährigen Männer eine Ausnahme darstellen und andere Jahrgänge im Jahr 2020 ein Maximum zeigen würden. Doch das trifft nicht zu. Kein einziger Jahrgang verzeichnete im Jahr 2020 ein Maximum. Im Gegenteil: Auch die 1-Jährigen, 2-Jährigen, 3-Jährigen, 9-Jährigen, 10-Jährigen, 15-Jährigen, 18-Jährigen und viele weitere männliche Jahrgänge hatten ihr Minimum im Jahr 2020. Dasselbe gilt bei den Frauen. Insgesamt hatten 31 Jahrgänge ihr Minimum im Jahr 2020. Wenn wir schließlich alle Jahrgänge in einer einzigen Grafik zusammenfassen, ergibt sich ein klares Bild: Das Minimum im Sterbegeschehen lag im Jahr 2020 (Grafik 3).
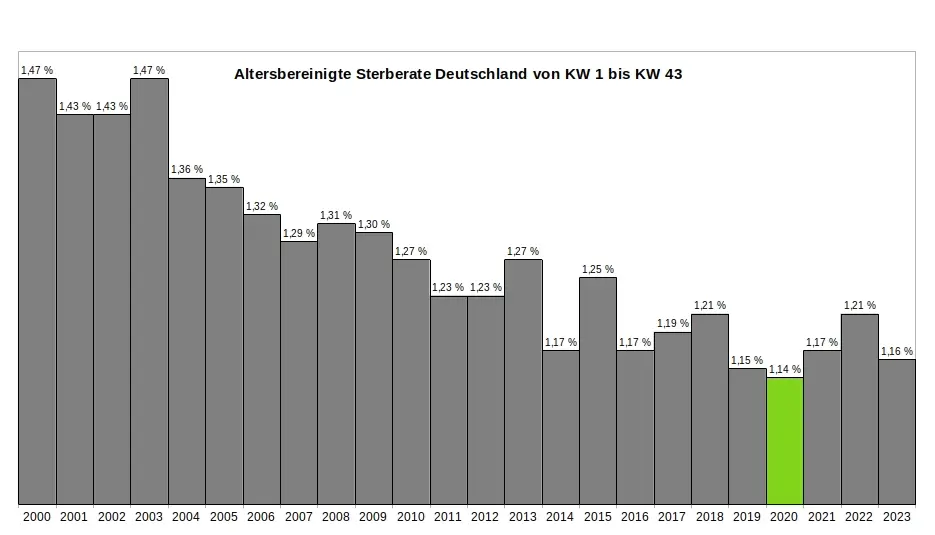
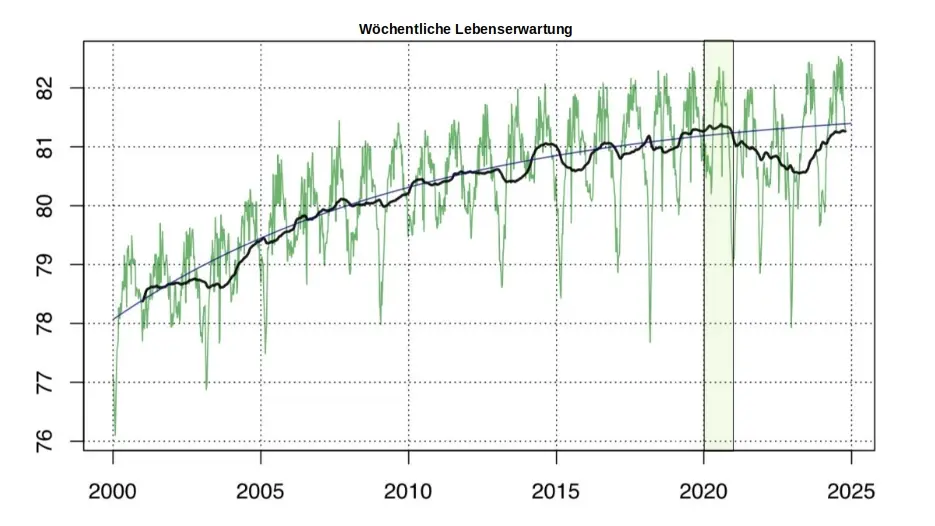
Ein kritischer Leser könnte nun wiederum vermuten, dass es innerhalb des Jahres 2020 möglicherweise starke Ausschläge nach oben bei einzelnen Jahrgängen gegeben haben könnte, die später durch Ausschläge nach unten ausgeglichen wurden – und dass diese Schwankungen in der jährlichen Übersicht nicht sichtbar sind. Doch auch das trifft nicht zu. Ein Blick auf die wöchentlichen Sterberaten zeigt, dass die ersten acht Monate der Pandemie keine nennenswerten Auffälligkeiten aufweisen. Es bleibt dabei: Die Rohdaten des Statistischen Bundesamtes bestätigen zweifelsfrei, dass die ersten acht Monate der Pandemie das historische Minimum im Sterbegeschehen darstellen. (Für die Fachleute sei angemerkt, dass im gleichen Zeitraum die Lebenserwartung die historischen Höchststände erreicht hatte – Grafik 4.)
So konstruierte das Amt aus einem Minimum ein Maximum:
Zur Erinnerung: Die Rohdaten des Statistischen Bundesamtes, die in den jährlichen Sterbetafeln zweifelsfrei dokumentiert sind, zeigen für das Jahr 2020 eindeutig ein Minimum im Sterbegeschehen. Aus diesen »in Stein gemeißelten« Zahlen ein Maximum zu »konstruieren«, ohne die Rohdaten selbst zu verändern, scheint auf den ersten Blick eine unlösbare Aufgabe. Jeder Student würde an einer solchen Herausforderung scheitern. Doch das Statistische Bundesamt hat einen kreativen Weg gefunden - ein Meisterstück gezielter Manipulation. In fünf Schritten zeigt sich, wie diese Täuschung der Öffentlichkeit umgesetzt wurde:
(1) Ignorieren der Sterberaten: Die präzisen, objektiven und leicht verständlichen Sterberaten aus den eigenen Sterbetafeln wurden konsequent ignoriert und verschwiegen. Diese Daten widersprachen dem gewünschten Narrativ und wurden daher gezielt ausgeklammert.
(2) Fokus auf absolute Todeszahlen: Die Aufmerksamkeit wurde stattdessen auf die absolute Zahl der Todesfälle gelenkt. Diese wirkt allein durch ihre schiere Größe dramatisch und emotionalisiert die Diskussion. Ein entscheidender Faktor wurde dabei ignoriert: Die absolute Zahl der Todesfälle steigt aufgrund der demografischen Entwicklung jedes Jahr an. Viele Menschen verstehen diesen Zusammenhang nicht und verbinden die steigenden Zahlen fälschlicherweise mit der vermeintlichen Pandemie.
(3) Einführung der Übersterblichkeit als neue Kennzahl: Erst ab Beginn der „Pandemie“ wurde die Kennzahl "Übersterblichkeit" eingeführt – und dies mit einer fragwürdigen Methode, die systematisch überhöhte Werte lieferte. Diese Kennzahl wurde regelmäßig, oft monatlich oder sogar wöchentlich, berechnet und diente als ständige Grundlage für alarmierende Schlagzeilen.
(4) Intensive Öffentlichkeitsarbeit: Durch eine breit angelegte Kampagne wurden die manipulativen Kennzahlen gezielt in den Fokus gerückt. Pressemitteilungen, Podcasts und öffentliche Auftritte konzentrierten sich fast ausschließlich auf die absoluten Todeszahlen und die Übersterblichkeit. Ziel war es, den Eindruck einer dramatischen Situation in der Öffentlichkeit zu verstärken.
(5) Bekämpfen kritischer Stimmen: Kritiker, die die Schwächen und manipulativen Aspekte dieser Methoden aufdeckten, wurden systematisch diskreditiert. Ihre Glaubwürdigkeit und Kompetenz wurden öffentlich infrage gestellt, um das sorgsam konstruierte Narrativ zu schützen.
Ohne diesen begleitenden Statistik-Betrug wäre das gesamte Pandemie-Theater meiner Meinung nach nicht möglich gewesen. Wer aus einem faktischen Minimum ein scheinbares Maximum "erschafft", handelt betrügerisch. Die Folgen dieses Betruges sind gravierend. Denken wir an die Angst, die in der Bevölkerung geschürt wurde – die Angst, bald sterben zu müssen. Denken wir an Masken, Abstandsregeln, isolierte ältere Menschen, Kinderimpfungen und all die Maßnahmen, die unter anderem auf diese falsche Statistik zurückgehen.
Wollen wir Bürger uns das gefallen lassen?
Wenn wir als Bürger zulassen, dass ein derart offensichtlicher und nachprüfbarer Täuschungsversuch ohne Konsequenzen bleibt, dann gefährdet das nicht nur die Integrität unserer Institutionen – es untergräbt das Fundament unserer Gesellschaft. In der DDR feierte man öffentlich Planerfüllung und Übererfüllung, während die Regale leer blieben. Damals wusste jeder: Statistik war ein Propagandainstrument. Niemand traute den Zahlen, die das Staatsfernsehen verkündete.
Während der Pandemie war es anders. Die Menschen vertrauten den Mitteilungen des Statistischen Bundesamtes und des RKI – blind. Die Enthüllungen durch den "RKI-Leak" haben gezeigt, dass auch das Robert-Koch-Institut nicht der Wissenschaft, sondern den Weisungen des Gesundheitsministers und militärischen Vorgaben folgte. Warum sollte es beim Statistischen Bundesamt anders gewesen sein? Diese Behörde ist dem Innenministerium unterstellt und somit ebenfalls weisungsgebunden.
Die Beweise für Täuschung liegen offen zutage. Es braucht keinen Whistleblower, keine geheimen Enthüllungen: Die Rohdaten des Statistischen Bundesamtes sprechen für sich. Sie sind öffentlich einsehbar – klar und unmissverständlich. Die Daten, die Tabellen, die Veröffentlichungen des Amtes selbst – sie sind die Anklageschrift. Sie zeigen, was wirklich war. Nicht mehr und nicht weniger.
Und wir? Was tun wir? Schweigen wir? Oder fordern wir endlich ein, was unser Recht ist? Wir Bürger dürfen das nicht hinnehmen. Es ist Zeit, unsere Behörden zur Rechenschaft zu ziehen. Diese Institutionen arbeiten nicht für sich – sie arbeiten für uns. Wir finanzieren sie, und wir haben das Recht, Transparenz und Verantwortung einzufordern. Manipulationen wie diese müssen aufgearbeitet werden und dürfen nie wieder geschehen. Die Strukturen, die solche Fehlentwicklungen in unseren Behörden ermöglicht haben, müssen offengelegt werden. Denn eine Demokratie lebt von Vertrauen – und Vertrauen muss verdient werden. Jeden Tag aufs Neue.
.
.
MARCEL BARZ, Jahrgang 1975, war Offizier der Bundeswehr und studierte Wirtschafts- und Organisationswissenschaften sowie Wirtschaftsinformatik. Er war Gründer und Geschäftsführer einer Softwarefirma, die sich auf Datenanalyse und Softwareentwicklung spezialisiert hatte. Im August 2021 veröffentlichte Barz den Videovortrag »Die Pandemie in den Rohdaten«, der über eine Million Aufrufe erzielte. Seitdem macht er als "Erbsenzähler" auf Widersprüche in amtlichen Statistiken aufmerksam.
-
 @ b8851a06:9b120ba1
2025-01-14 15:28:32
@ b8851a06:9b120ba1
2025-01-14 15:28:32It Begins with a Click
It starts with a click: “Do you agree to our terms and conditions?”\ You scroll, you click, you comply. A harmless act, right? But what if every click was a surrender? What if every "yes" was another link in the chain binding you to a life where freedom requires approval?
This is the age of permission. Every aspect of your life is mediated by gatekeepers. Governments demand forms, corporations demand clicks, and algorithms demand obedience. You’re free, of course, as long as you play by the rules. But who writes the rules? Who decides what’s allowed? Who owns your life?
Welcome to Digital Serfdom
We once imagined the internet as a digital frontier—a vast, open space where ideas could flow freely and innovation would know no bounds. But instead of creating a decentralized utopia, we built a new feudal system.
- Your data? Owned by the lords of Big Tech.
- Your money? Controlled by banks and bureaucrats who can freeze it on a whim.
- Your thoughts? Filtered by algorithms that reward conformity and punish dissent.
The modern internet is a land of serfs and lords, and guess who’s doing the farming? You. Every time you agree to the terms, accept the permissions, or let an algorithm decide for you, you till the fields of a system designed to control, not liberate.
They don’t call it control, of course. They call it “protection.” They say, “We’re keeping you safe,” as they build a cage so big you can’t see the bars.
Freedom in Chains
But let’s be honest: we’re not just victims of this system—we’re participants. We’ve traded freedom for convenience, sovereignty for security. It’s easier to click “I Agree” than to read the fine print. It’s easier to let someone else hold your money than to take responsibility for it yourself. It’s easier to live a life of quiet compliance than to risk the chaos of true independence.
We tell ourselves it’s no big deal. What’s one click? What’s one form? But the permissions pile up. The chains grow heavier. And one day, you wake up and realize you’re free to do exactly what the system allows—and nothing more.
The Great Unpermissioning
It doesn’t have to be this way. You don’t need their approval. You don’t need their systems. You don’t need their permission.
The Great Unpermissioning is not a movement—it’s a mindset. It’s the refusal to accept a life mediated by gatekeepers. It’s the quiet rebellion of saying, “No.” It’s the realization that the freedom you seek won’t be granted—it must be reclaimed.
- Stop asking. Permission is their tool. Refusal is your weapon.
- Start building. Embrace tools that decentralize power: Bitcoin, encryption, open-source software, decentralized communication. Build systems they can’t control.
- Stand firm. They’ll tell you it’s dangerous. They’ll call you a radical. But remember: the most dangerous thing you can do is comply.
The path won’t be easy. Freedom never is. But it will be worth it.
The New Frontier
The age of permission has turned us into digital serfs, but there’s a new frontier on the horizon. It’s a world where you control your money, your data, your decisions. It’s a world of encryption, anonymity, and sovereignty. It’s a world built not on permission but on principles.
This world won’t be given to you. You have to build it. You have to fight for it. And it starts with one simple act: refusing to comply.
A Final Word
They promised us safety, but what they delivered was submission. The age of permission has enslaved us to the mundane, the monitored, and the mediocre. The Great Unpermissioning isn’t about tearing down the old world—it’s about walking away from it.
You don’t need to wait for their approval. You don’t need to ask for their permission. The freedom you’re looking for is already yours. Permission is their power—refusal is yours.
-
 @ eac63075:b4988b48
2025-01-04 19:41:34
@ eac63075:b4988b48
2025-01-04 19:41:34Since its creation in 2009, Bitcoin has symbolized innovation and resilience. However, from time to time, alarmist narratives arise about emerging technologies that could "break" its security. Among these, quantum computing stands out as one of the most recurrent. But does quantum computing truly threaten Bitcoin? And more importantly, what is the community doing to ensure the protocol remains invulnerable?
The answer, contrary to sensationalist headlines, is reassuring: Bitcoin is secure, and the community is already preparing for a future where quantum computing becomes a practical reality. Let’s dive into this topic to understand why the concerns are exaggerated and how the development of BIP-360 demonstrates that Bitcoin is one step ahead.
What Is Quantum Computing, and Why Is Bitcoin Not Threatened?
Quantum computing leverages principles of quantum mechanics to perform calculations that, in theory, could exponentially surpass classical computers—and it has nothing to do with what so-called “quantum coaches” teach to scam the uninformed. One of the concerns is that this technology could compromise two key aspects of Bitcoin’s security:
- Wallets: These use elliptic curve algorithms (ECDSA) to protect private keys. A sufficiently powerful quantum computer could deduce a private key from its public key.
- Mining: This is based on the SHA-256 algorithm, which secures the consensus process. A quantum attack could, in theory, compromise the proof-of-work mechanism.
Understanding Quantum Computing’s Attack Priorities
While quantum computing is often presented as a threat to Bitcoin, not all parts of the network are equally vulnerable. Theoretical attacks would be prioritized based on two main factors: ease of execution and potential reward. This creates two categories of attacks:
1. Attacks on Wallets
Bitcoin wallets, secured by elliptic curve algorithms, would be the initial targets due to the relative vulnerability of their public keys, especially those already exposed on the blockchain. Two attack scenarios stand out:
-
Short-term attacks: These occur during the interval between sending a transaction and its inclusion in a block (approximately 10 minutes). A quantum computer could intercept the exposed public key and derive the corresponding private key to redirect funds by creating a transaction with higher fees.
-
Long-term attacks: These focus on old wallets whose public keys are permanently exposed. Wallets associated with Satoshi Nakamoto, for example, are especially vulnerable because they were created before the practice of using hashes to mask public keys.
We can infer a priority order for how such attacks might occur based on urgency and importance.
 Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)
Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)2. Attacks on Mining
Targeting the SHA-256 algorithm, which secures the mining process, would be the next objective. However, this is far more complex and requires a level of quantum computational power that is currently non-existent and far from realization. A successful attack would allow for the recalculation of all possible hashes to dominate the consensus process and potentially "mine" it instantly.
 Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin Attacks
Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin AttacksRecently, Narcelio asked me about a statement I made on Tubacast:
https://x.com/eddieoz/status/1868371296683511969
If an attack became a reality before Bitcoin was prepared, it would be necessary to define the last block prior to the attack and proceed from there using a new hashing algorithm. The solution would resemble the response to the infamous 2013 bug. It’s a fact that this would cause market panic, and Bitcoin's price would drop significantly, creating a potential opportunity for the well-informed.
Preferably, if developers could anticipate the threat and had time to work on a solution and build consensus before an attack, they would simply decide on a future block for the fork, which would then adopt the new algorithm. It might even rehash previous blocks (reaching consensus on them) to avoid potential reorganization through the re-mining of blocks using the old hash. (I often use the term "shielding" old transactions).
How Can Users Protect Themselves?
While quantum computing is still far from being a practical threat, some simple measures can already protect users against hypothetical scenarios:
- Avoid using exposed public keys: Ensure funds sent to old wallets are transferred to new ones that use public key hashes. This reduces the risk of long-term attacks.
- Use modern wallets: Opt for wallets compatible with SegWit or Taproot, which implement better security practices.
- Monitor security updates: Stay informed about updates from the Bitcoin community, such as the implementation of BIP-360, which will introduce quantum-resistant addresses.
- Do not reuse addresses: Every transaction should be associated with a new address to minimize the risk of repeated exposure of the same public key.
- Adopt secure backup practices: Create offline backups of private keys and seeds in secure locations, protected from unauthorized access.
BIP-360 and Bitcoin’s Preparation for the Future
Even though quantum computing is still beyond practical reach, the Bitcoin community is not standing still. A concrete example is BIP-360, a proposal that establishes the technical framework to make wallets resistant to quantum attacks.
BIP-360 addresses three main pillars:
- Introduction of quantum-resistant addresses: A new address format starting with "BC1R" will be used. These addresses will be compatible with post-quantum algorithms, ensuring that stored funds are protected from future attacks.
- Compatibility with the current ecosystem: The proposal allows users to transfer funds from old addresses to new ones without requiring drastic changes to the network infrastructure.
- Flexibility for future updates: BIP-360 does not limit the choice of specific algorithms. Instead, it serves as a foundation for implementing new post-quantum algorithms as technology evolves.
This proposal demonstrates how Bitcoin can adapt to emerging threats without compromising its decentralized structure.
Post-Quantum Algorithms: The Future of Bitcoin Cryptography
The community is exploring various algorithms to protect Bitcoin from quantum attacks. Among the most discussed are:
- Falcon: A solution combining smaller public keys with compact digital signatures. Although it has been tested in limited scenarios, it still faces scalability and performance challenges.
- Sphincs: Hash-based, this algorithm is renowned for its resilience, but its signatures can be extremely large, making it less efficient for networks like Bitcoin’s blockchain.
- Lamport: Created in 1977, it’s considered one of the earliest post-quantum security solutions. Despite its reliability, its gigantic public keys (16,000 bytes) make it impractical and costly for Bitcoin.
Two technologies show great promise and are well-regarded by the community:
- Lattice-Based Cryptography: Considered one of the most promising, it uses complex mathematical structures to create systems nearly immune to quantum computing. Its implementation is still in its early stages, but the community is optimistic.
- Supersingular Elliptic Curve Isogeny: These are very recent digital signature algorithms and require extensive study and testing before being ready for practical market use.
The final choice of algorithm will depend on factors such as efficiency, cost, and integration capability with the current system. Additionally, it is preferable that these algorithms are standardized before implementation, a process that may take up to 10 years.
Why Quantum Computing Is Far from Being a Threat
The alarmist narrative about quantum computing overlooks the technical and practical challenges that still need to be overcome. Among them:
- Insufficient number of qubits: Current quantum computers have only a few hundred qubits, whereas successful attacks would require millions.
- High error rate: Quantum stability remains a barrier to reliable large-scale operations.
- High costs: Building and operating large-scale quantum computers requires massive investments, limiting their use to scientific or specific applications.
Moreover, even if quantum computers make significant advancements, Bitcoin is already adapting to ensure its infrastructure is prepared to respond.
Conclusion: Bitcoin’s Secure Future
Despite advancements in quantum computing, the reality is that Bitcoin is far from being threatened. Its security is ensured not only by its robust architecture but also by the community’s constant efforts to anticipate and mitigate challenges.
The implementation of BIP-360 and the pursuit of post-quantum algorithms demonstrate that Bitcoin is not only resilient but also proactive. By adopting practical measures, such as using modern wallets and migrating to quantum-resistant addresses, users can further protect themselves against potential threats.
Bitcoin’s future is not at risk—it is being carefully shaped to withstand any emerging technology, including quantum computing.
-
 @ b8851a06:9b120ba1
2025-01-14 10:56:55
@ b8851a06:9b120ba1
2025-01-14 10:56:55Starting in January 2025, the EU’s MiCA regulation enforced strict KYC requirements, especially for Bitcoin transactions over €1,000 between exchanges and self-hosted wallets. While this creates new challenges, there are still legitimate ways to protect your privacy and maintain control over your Bitcoin.
Effective Privacy Solutions
-
Take Control with Self-Custody • Run Your Own Node: This ensures you’re not relying on third-party servers, giving you full control of your transactions. • Use Fresh Addresses: Always generate a new address for each transaction to keep your activity private and harder to trace. • Choose the Right Wallets: Use wallets like #Sparrow or #Wasabi, which let you connect directly to your own node for added privacy (check if there are any legal cases against any wallet before you use one.).
-
Leverage the Lightning Network • Keep Transactions Off-Chain: Lightning lets you make payments without broadcasting them to the blockchain. • #Onion Routing for Privacy: This hides your payment path, protecting both you and the recipient. • Hard-to-Trace Payments: With multiple hops between nodes, tracking transactions becomes nearly impossible.
-
Smarter Transaction Habits • Keep Channels Open: By leaving your #Lightning payment channels open, you minimize on-chain activity. • Use Public Channels Wisely: Multiple public channels provide plausible deniability. • Go Private with Unannounced Channels: For maximum privacy, consider private payment channels.
How to Implement These Tools
-
Setting Up the Lightning Network • Privacy-First Funding: When funding your channels, use methods like #CoinJoin to enhance privacy. • Better Receiver Privacy: Use tools like #Voltage Flow 2.0 for added anonymity when receiving payments. • Stay on Top of Channel Management: Properly manage your payment channels to avoid privacy leaks.
-
Strengthen Your Operational Security • Avoid Reusing Addresses: Reusing the same wallet address makes it easier to trace your transactions. • Separate Public and Private Transactions: Keep identified funds and private wallets completely separate. • Use Tor or VPNs: Always use privacy tools like Tor or a #VPN when accessing Bitcoin wallets or services.
Staying Safe
-
Legal Awareness • Mind the Limits: Be cautious with transactions over €1,000, as they’ll trigger reporting requirements. • Peer-to-Peer Freedom: Transactions between unhosted wallets remain outside #MiCA ’s reach, so direct transfers are still an option. • Check Local Rules: Privacy tool regulations vary between countries, so make sure you’re up to speed on what’s allowed where you live.
-
Practical Safeguards • Double-Check Everything: Always verify wallet addresses before sending funds to avoid costly mistakes. • Stay Updated: Keep your wallets, nodes, and security tools current with the latest updates. • Keep Offline Backups: Store your recovery phrases and backups somewhere secure and offline.
Bitcoin #privacy isn’t automatic—it takes effort and vigilance. But by following these steps, you can stay in control of your financial freedom even in an increasingly regulated world. Stay informed, make smart decisions, and build habits that protect your privacy.
Disclaimer:
This post is for educational purposes only and is not financial, legal, or investment advice. The tools and techniques shared here are not meant to help anyone break the law or avoid regulations. You’re responsible on complying with local laws and consult legal professionals if you’re unsure about anything.
The goal is to inform and empower you to take control of your privacy responsibly.
Stay safe and stay free.
-
-
 @ 6be5cc06:5259daf0
2024-12-29 19:54:14
@ 6be5cc06:5259daf0
2024-12-29 19:54:14Um dos padrões mais bem estabelecidos ao medir a opinião pública é que cada geração tende a seguir um caminho semelhante em termos de política e ideologia geral. Seus membros compartilham das mesmas experiências formativas, atingem os marcos importantes da vida ao mesmo tempo e convivem nos mesmos espaços. Então, como devemos entender os relatórios que mostram que a Geração Z é hiperprogressista em certos assuntos, mas surpreendentemente conservadora em outros?
A resposta, nas palavras de Alice Evans, pesquisadora visitante na Universidade de Stanford e uma das principais estudiosas do tema, é que os jovens de hoje estão passando por um grande divergência de gênero, com as jovens mulheres do primeiro grupo e os jovens homens do segundo. A Geração Z representa duas gerações, e não apenas uma.
Em países de todos os continentes, surgiu um distanciamento ideológico entre jovens homens e mulheres. Milhões de pessoas que compartilham das mesmas cidades, locais de trabalho, salas de aula e até casas, não veem mais as coisas da mesma maneira.
Nos Estados Unidos, os dados da Gallup mostram que, após décadas em que os sexos estavam distribuídos de forma relativamente equilibrada entre visões políticas liberais e conservadoras, as mulheres entre 18 e 30 anos são agora 30 pontos percentuais mais liberais do que os homens dessa faixa etária. Essa diferença surgiu em apenas seis anos.
A Alemanha também apresenta um distanciamento de 30 pontos entre homens jovens conservadores e mulheres jovens progressistas, e no Reino Unido, a diferença é de 25 pontos. Na Polônia, no ano passado, quase metade dos homens entre 18 e 21 anos apoiou o partido de extrema direita Confederation, em contraste com apenas um sexto das jovens mulheres dessa mesma idade.
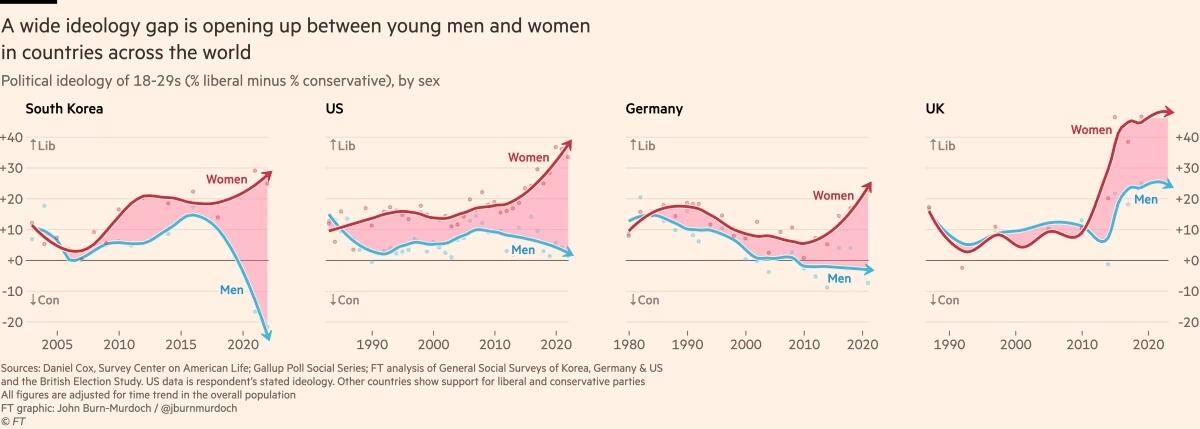
Fora do Ocidente, há divisões ainda mais acentuadas. Na Coreia do Sul, há um enorme abismo entre homens e mulheres jovens, e a situação é semelhante na China. Na África, a Tunísia apresenta o mesmo padrão. Vale notar que em todos os países essa divisão drástica ocorre principalmente entre a geração mais jovem, sendo muito menos pronunciada entre homens e mulheres na faixa dos 30 anos ou mais velhos.
O movimento # MeToo foi o principal estopim, trazendo à tona valores feministas intensos entre jovens mulheres que se sentiram empoderadas para denunciar injustiças de longa data. Esse estopim encontrou especialmente terreno fértil na Coreia do Sul, onde a desigualdade de gênero é bastante visível e a misoginia explícita é comum. (palavras da Financial Times, eu só traduzi)
Na eleição presidencial da Coreia do Sul em 2022, enquanto homens e mulheres mais velhos votaram de forma unificada, os jovens homens apoiaram fortemente o partido de direita People Power, enquanto as jovens mulheres apoiaram o partido liberal Democratic em números quase iguais e opostos.
A situação na Coreia é extrema, mas serve como um alerta para outros países sobre o que pode acontecer quando jovens homens e mulheres se distanciam. A sociedade está dividida, a taxa de casamento despencou e a taxa de natalidade caiu drasticamente, chegando a 0,78 filhos por mulher em 2022, o menor número no mundo todo.
Sete anos após a explosão inicial do movimento # MeToo, a divergência de gênero em atitudes tornou-se autossustentável.
Dados das pesquisas mostram que em muitos países, as diferenças ideológicas vão além dessa questão específica. A divisão progressista-conservadora sobre assédio sexual parece ter causado ou pelo menos faz parte de um alinhamento mais amplo, em que jovens homens e mulheres estão se organizando em grupos conservadores e liberais em outros assuntos.
Nos EUA, Reino Unido e Alemanha, as jovens mulheres agora adotam posturas mais liberais sobre temas como imigração e justiça racial, enquanto grupos etários mais velhos permanecem equilibrados. A tendência na maioria dos países tem sido de mulheres se inclinando mais para a esquerda, enquanto os homens permanecem estáveis. No entanto, há sinais de que os jovens homens estão se movendo para a direita na Alemanha, tornando-se mais críticos em relação à imigração e se aproximando do partido de extrema direita AfD nos últimos anos.
Seria fácil dizer que tudo isso é apenas uma fase passageira, mas os abismos ideológicos apenas crescem, e os dados mostram que as experiências políticas formativas das pessoas são difíceis de mudar. Tudo isso é agravado pelo fato de que o aumento dos smartphones e das redes sociais faz com que os jovens homens e mulheres agora vivam em espaços separados e tenham culturas distintas.
As opiniões dos jovens frequentemente são ignoradas devido à baixa participação política, mas essa mudança pode deixar consequências duradouras, impactando muito mais do que apenas os resultados das eleições.
Retirado de: https://www.ft.com/content/29fd9b5c-2f35-41bf-9d4c-994db4e12998
-
 @ c631e267:c2b78d3e
2025-01-18 09:34:51
@ c631e267:c2b78d3e
2025-01-18 09:34:51Die grauenvollste Aussicht ist die der Technokratie – \ einer kontrollierenden Herrschaft, \ die durch verstümmelte und verstümmelnde Geister ausgeübt wird. \ Ernst Jünger
«Davos ist nicht mehr sexy», das Weltwirtschaftsforum (WEF) mache Davos kaputt, diese Aussagen eines Einheimischen las ich kürzlich in der Handelszeitung. Während sich einige vor Ort enorm an der «teuersten Gewerbeausstellung der Welt» bereicherten, würden die negativen Begleiterscheinungen wie Wohnungsnot und Niedergang der lokalen Wirtschaft immer deutlicher.
Nächsten Montag beginnt in dem Schweizer Bergdorf erneut ein Jahrestreffen dieses elitären Clubs der Konzerne, bei dem man mit hochrangigen Politikern aus aller Welt und ausgewählten Vertretern der Systemmedien zusammenhocken wird. Wie bereits in den vergangenen vier Jahren wird die Präsidentin der EU-Kommission, Ursula von der Leyen, in Begleitung von Klaus Schwab ihre Grundsatzansprache halten.
Der deutsche WEF-Gründer hatte bei dieser Gelegenheit immer höchst lobende Worte für seine Landsmännin: 2021 erklärte er sich «stolz, dass Europa wieder unter Ihrer Führung steht» und 2022 fand er es bemerkenswert, was sie erreicht habe angesichts des «erstaunlichen Wandels», den die Welt in den vorangegangenen zwei Jahren erlebt habe; es gebe nun einen «neuen europäischen Geist».
Von der Leyens Handeln während der sogenannten Corona-«Pandemie» lobte Schwab damals bereits ebenso, wie es diese Woche das Karlspreis-Direktorium tat, als man der Beschuldigten im Fall Pfizergate die diesjährige internationale Auszeichnung «für Verdienste um die europäische Einigung» verlieh. Außerdem habe sie die EU nicht nur gegen den «Aggressor Russland», sondern auch gegen die «innere Bedrohung durch Rassisten und Demagogen» sowie gegen den Klimawandel verteidigt.
Jene Herausforderungen durch «Krisen epochalen Ausmaßes» werden indes aus dem Umfeld des WEF nicht nur herbeigeredet – wie man alljährlich zur Zeit des Davoser Treffens im Global Risks Report nachlesen kann, der zusammen mit dem Versicherungskonzern Zurich erstellt wird. Seit die Globalisten 2020/21 in der Praxis gesehen haben, wie gut eine konzertierte und konsequente Angst-Kampagne funktionieren kann, geht es Schlag auf Schlag. Sie setzen alles daran, Schwabs goldenes Zeitfenster des «Great Reset» zu nutzen.
Ziel dieses «großen Umbruchs» ist die totale Kontrolle der Technokraten über die Menschen unter dem Deckmantel einer globalen Gesundheitsfürsorge. Wie aber könnte man so etwas erreichen? Ein Mittel dazu ist die «kreative Zerstörung». Weitere unabdingbare Werkzeug sind die Einbindung, ja Gleichschaltung der Medien und der Justiz.
Ein «Great Mental Reset» sei die Voraussetzung dafür, dass ein Großteil der Menschen Einschränkungen und Manipulationen wie durch die Corona-Maßnahmen praktisch kritik- und widerstandslos hinnehme, sagt der Mediziner und Molekulargenetiker Michael Nehls. Er meint damit eine regelrechte Umprogrammierung des Gehirns, wodurch nach und nach unsere Individualität und unser soziales Bewusstsein eliminiert und durch unreflektierten Konformismus ersetzt werden.
Der aktuelle Zustand unserer Gesellschaften ist auch für den Schweizer Rechtsanwalt Philipp Kruse alarmierend. Durch den Umgang mit der «Pandemie» sieht er die Grundlagen von Recht und Vernunft erschüttert, die Rechtsstaatlichkeit stehe auf dem Prüfstand. Seiner dringenden Mahnung an alle Bürger, die Prinzipien von Recht und Freiheit zu verteidigen, kann ich mich nur anschließen.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ e3168078:10f13b2c
2025-01-21 15:44:45
@ e3168078:10f13b2c
2025-01-21 15:44:45ノス!
最近Umbrel上のn8nを使ってstacker newsの記事を要約するNostr botを作ってみました。
その際にFirecrawlというスクレイピングのSaaSを使っていたんですがセルフホストできるようなので試してみました。
Firecrawlは動的なページも読めたりマークダウンへの変換をしてくれますが無料プランだと1ヶ月500ページの制限があり、セルフホストすれば気兼ねなく使えます!
今回はUmbrel上のPortainerというアプリを使ってFirecrawlを動かせたのでその記録です。手順
まずはUmbrelにPortainerアプリをインストールします。 Poratinerは今回初めて使ったんですが独自のDockerコンテナをUmbrelで動かす際に推奨されているアプリのようです。

アプリを開いてパスワードの初期設定などを済ませるとダッシュボードが表示されるかと思います。 ここでStackという機能を使ってFirecrawlのDocker composeを一括で取り込むことができます。
新しいStackを作成する画面で以下を入力します。
Repository URL: https://github.com/mendableai/firecrawl
Repository reference: refs/heads/main
Compose path: docker-compose.yaml (デフォルトがymlになっててハマりました…)
上記に加えてenv varを設定する必要があるんですがPortainerでは上記の画像下部にあるように "Load Variables from .env file" からenvファイルを選択できます。 Firecrawlのgithubにあるように apps/api/.env.example をダウンロードし以下の内容を更新しPortainerに取り込ませます。
USE_DB_AUTHENTICATION=false TEST_API_KEY=fc-test-keyあとはDeploy the stackを押して少し待つとfirecrawlのセットアップ完了です。
確認
動作テストにはUmbrelの設定からAdvanced Settings -> Terminal -> Umbrel OSを開き以下のコマンドを実行ししマークダウンが返って来れば成功です。
$ curl -X POST http://localhost:3002/v1/scrape -H 'Authorization: Bearer fc-test-key' -H 'Content-Type: application/json' -d '{ "url": "https://example.com", "formats": ["markdown"] }' {"success":true,"data":{"markdown":"Example Domain\n==============\n\nThis domain is for use in illustrative examples in documents. You may use this domain in literature without prior coordination or asking for permission.\n\n[More information...](https://www.iana.org/domains/example)","metadata":{"title":"Example Domain","ogLocaleAlternate":[],"scrapeId":"7c196348-6561-4ebb-bb8a-9121a29c64b5","viewport":"width=device-width, initial-scale=1","sourceURL":"https://example.com","url":"https://example.com/","statusCode":200}}}またn8n等のUmbrelの他のアプリ(コンテナ)から利用する場合はlocalhostがコンテナ自身になってしまうので別のIP等(172.17.0.1)を使う必要があるのでご注意ください。 (参考)
以上でUmbrel上でのFirecrawlセルフホストができるようになりn8nからも制限なく使えるようになりました。
-
 @ f9cf4e94:96abc355
2025-01-18 06:09:50
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |
 | Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |
| Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |  | 16Gb |
| 16Gb |Recomendo que use o Ubuntu Server para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi aqui. O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível aqui. Não instale um desktop (como xubuntu, lubuntu, xfce, etc.).
Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
bash apt update apt install tor
Passo 2: Criar o Arquivo de Serviço
nrs.service🔧Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit [Unit] Description=Nostr Relay Server Service After=network.target
[Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure
[Install] WantedBy=multi-user.target ```
Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr aqui no GitHub.
Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
bash mkdir -p /opt/nrs /mnt/edriver
Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
bash lsblk
Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo,
/dev/sda) e formate-o:bash mkfs.vfat /dev/sda
Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta
/mnt/edriver:bash mount /dev/sda /mnt/edriver
Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
bash blkid
Passo 9: Alterar o
fstabpara Montar o Pendrive Automáticamente 📝Abra o arquivo
/etc/fstabe adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta
/opt/nrs:bash cp nrs-arm64 /opt/nrs
Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em
/opt/nrs/config.yaml:yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true
Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo
nrs.servicepara o diretório/etc/systemd/system/:bash cp nrs.service /etc/systemd/system/Recarregue os serviços e inicie o serviço
nrs:bash systemctl daemon-reload systemctl enable --now nrs.service
Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor
/var/lib/tor/torrce adicione a seguinte linha:torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334
Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
bash systemctl enable --now tor.serviceO Tor irá gerar um endereço
.onionpara o seu servidor Nostr. Você pode encontrá-lo no arquivo/var/lib/tor/nostr_server/hostname.
Observações ⚠️
- Com essa configuração, os dados serão salvos no pendrive, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço
.oniondo seu servidor Nostr será algo como:ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion.
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-
 @ 6f3670d9:03f04036
2024-12-29 08:20:22
@ 6f3670d9:03f04036
2024-12-29 08:20:22Disclaimer: - This will void your warranty - There might be differences between the Bitaxe and the Lucky Miner that might not cause issues or damage immediately, but might manifest long-term - Proceed at your own risk
A Different Pickaxe
You live in a place where it's difficult to get a Bitaxe. You have access to AliExpress. You look around. You find something called the "Lucky Miner LV06". A Bitaxe clone that uses the same mining chip as the Bitaxe Ultra (BM1366 ASIC). You buy one.
You plug it in, you enter your wallet address and other settings, and it starts mining. It works! Great!
But it's running a customized firmware. It's not AxeOS. Maybe there's something shady in the stock firmware. It's not open-source, after all. Also, AxeOS looks amazing... And that automatic pool fail-over feature is handy.
You think to yourself: "Maybe I can use the Bitaxe firmware on this?". Guess what? You're right!
Flashing From Web UI
What usually works for me is to: - Download the Bitaxe firmware files (
esp-miner.binandwww.bin) from GitHub (here). Version 2.4.1 seems to work well, as of this writing. - Then from the Lucky Miner web interface, upload the "Website" (www.bin) file. - Wait for a minute or two after it's done uploading. - Upload the "Firmware" (esp-miner.bin) file. - Wait another minute or two. - Unplug the power and plug it back in. - Set the "Core Voltage" and "Frequency" to the defaults. - Unplug the power and plug it back in again.If you're lucky (no pun intended), you'll have a working Lucky Miner with AxeOS. Update the settings and mine away!
However, often times I've been unlucky, like what happened while I was writing this article, ironically. The miner malfunctions for no obvious reason. It keeps rebooting, or it's not mining (zero/low hashrate), or the web interface is inaccessible. You name it.
The miner has become a "brick". How do you "unbrick" it?
When you brick a Bitaxe, you can recover it by flashing (uploading) a "Factory Image". The Bitaxe has a USB port that makes this easy. Follow the guide and it should come back to life again. Unfortunately, the Lucky Miner LV06 doesn't have a USB port. It has a serial port, though. We'll have to get our hands a bit dirty.
Flashing Using the Serial Port
We need to connect the serial port of the miner to a computer and run a program to flash (upload) the firmware file on the miner. Any 3.3v UART serial port should be sufficient. Unfortunately, PCs don't usually come with a UART serial port these days, let alone a 3.3v one. The serial port common in old computers is an RS-232 port, which will most probably fry your miner if you try to connect it directly. Beware.
In my case, as a serial port for my PC, I'm using an Arduino Due I had lying around. We connect it to the PC through USB, and on the other side we connect a few wires to the miner, which gives the PC access to the miner.
WARNING: Make sure your serial port is 3.3v or you will probably kill the miner. Arduino Uno is 5v not 3.3v, for example, and cannot be used for this.
Wiring
First, we need to open the Lucky Miner. Use a small flat screwdriver to gently push the two plastic clips shown in the picture below. Gently pry the top cover away from the bottom cover on the clips side first, then remove the other side. Be careful not to break the display cable.
Once the cover is off, you can find the miner's serial port in the top right corner (J10), as shown in the next picture. We'll also need the reset button (EN).
There are three screws holding the PCB and the bottom cover together. If you're confident in your ability to push the small button on the underside of the PCB with the bottom cover on, then no need to remove these. The following picture shows what we need from that side.
And the next picture shows the pins and USB port we will use from the Arduino.
Now, we need to connect: - The USB port on the Arduino labelled "programming" to the PC - Pin 18 (TX1) on the Arduino to J10 through-hole pad 5 (blue dot) - Pin 19 (RX1) on the Arduino to J10 through-hole pad 3 (green dot) - Any GND pin on the Arduino to J10 through-hole pad 4 (yellow dot)
I didn't need to solder the wires to the pads. Keeping everything stable, perhaps by putting a weight on the wires or a bit of tape, was sufficient in all my attempts.
Setting up the Arduino
To use the Arduino as a serial port for our PC, we'll have to make it pass-through data back and forth between the USB port and UART1, where we connected the miner.
The following steps are all done on a PC running Debian Linux (Bookworm), in the spirit of freedom and open-source.
First, we start the Arduino IDE. If the package for the Arduino Due board is not already installed, you'll see a small prompt at the bottom. Click "Install this package".
Click the "Install" button.
Once the package is installed, click "Close".
Next, we select the Due board. Click the "Tools" menu, select "Board", select "Arduino ARM (32-bits) Boards" and click "Arduino Due (Programming Port)"
Next, we select the port. Click the "Tools" menu again, select "Port", and click the port where the Arduino is connected. In my case it was "/dev/ttyACM0".
Now we need to upload the following code to the Arduino board. The code is actually the "SerialPassthrough" example from the IDE, but with the serial speed changed to match the miner.
``` void setup() { Serial.begin(115200); Serial1.begin(115200); }
void loop() { if (Serial.available()) { // If anything comes in Serial (USB), Serial1.write(Serial.read()); // read it and send it out Serial1 }
if (Serial1.available()) { // If anything comes in Serial1 Serial.write(Serial1.read()); // read it and send it out Serial (USB) } } ```
Copy/paste the code into the IDE and click upload. You'll see "Done uploading" at the bottom.
Next we'll test if we're receiving data from the miner. We start by opening the "Serial Monitor" from the "Tools" menu in the IDE. Then we change the baudrate to 115200.
Set the Arduino and the miner in a comfortable position, make sure the wires are held in place and got a good contact on both sides, and the power is plugged in.
Now we'll put the miner in "download" mode. Press and hold the button on the underside (K1), press and release the reset button (EN), then release the other button (K1).
You should see some text from the miner in the serial monitor window, like in the picture below.
Congratulations! We know we're able to receive data from the miner now. We're not sure transmit is working, but we'll find out when we try to flash.
Flashing Using the Serial Port, for Real
To flash the Lucky Miner we'll need a software tool named esptool and the factory image firmware file.
I usually use "esp-miner-factory-205-v2.1.8.bin" for the factory image (this one) as a base, and then flash the version I want from the Web UI, using the steps I mentioned earlier.
For esptool, the documentation (here) shows us how to install it. To make things a little easier on our Debian Linux system, we'll use pipx instead of pip. The instructions below are adapted for that.
First we make sure pipx is installed. Run this command in a terminal and follow the instructions:
sudo apt-get install pipxThen we install esptool using pipx. Run the following in a terminal:
pipx install esptoolThe output will be something like this:
user@pc:~$ pipx install esptool installed package esptool 4.8.1, installed using Python 3.11.2 These apps are now globally available - esp_rfc2217_server.py - espefuse.py - espsecure.py - esptool.py ⚠️ Note: '/home/user/.local/bin' is not on your PATH environment variable. These apps will not be globally accessible until your PATH is updated. Run `pipx ensurepath` to automatically add it, or manually modify your PATH in your shell's config file (i.e. ~/.bashrc). done! ✨ 🌟 ✨We can see pipx telling us we won't be able to run our tool because the folder where it was installed is not in the PATH variable. To fix that, we can follow pipx instructions and run:
pipx ensurepathAnd we'll see something like this:
``` user@pc:~$ pipx ensurepath Success! Added /home/user/.local/bin to the PATH environment variable.
Consider adding shell completions for pipx. Run 'pipx completions' for instructions.
You will need to open a new terminal or re-login for the PATH changes to take effect.
Otherwise pipx is ready to go! ✨ 🌟 ✨ ```
Now, close the terminal and re-open it so that esptool becomes available.
Finally, to actually flash the miner, put the miner in download mode, then in the following command change the port ("/dev/ttyACM0") to your serial port, as we've seen earlier, and the file path to where your firmware file is, and run it:
esptool.py -p /dev/ttyACM0 --baud 115200 write_flash --erase-all 0x0 ~/Downloads/esp-miner-factory-205-v2.1.8.binIf everything went fine, the tool will take a few minutes to flash the firmware to the miner. You'll see something like this in the output:
``` user@pc:~$ esptool.py -p /dev/ttyACM0 --baud 115200 write_flash --erase-all 0x0 ~/Downloads/esp-miner-factory-205-v2.1.8.bin esptool.py v4.8.1 Serial port /dev/ttyACM0 Connecting..... Detecting chip type... ESP32-S3 Chip is ESP32-S3 (QFN56) (revision v0.2) Features: WiFi, BLE, Embedded PSRAM 8MB (AP_3v3) Crystal is 40MHz MAC: 3c:84:27:ba:be:01 Uploading stub... Running stub... Stub running... Configuring flash size... Erasing flash (this may take a while)... Chip erase completed successfully in 9.5s Compressed 15802368 bytes to 1320190... Wrote 15802368 bytes (1320190 compressed) at 0x00000000 in 152.1 seconds (effective 831.2 kbit/s)... Hash of data verified.
Leaving... Hard resetting via RTS pin... ```
And we're done! Hopefully the miner will be recovered now.
Hope this helps!
Stay humble,
dumb-packageA Warning About Beta Versions of AxeOS
For reasons unknown to me, while I was writing this article I wanted to try the testing version of AxeOS, which was v2.4.1b (beta). Flashing from Web UI went smooth, but the miner stopped mining. I flashed back to v2.1.8 using the serial port, a known good version for me, but it wouldn't mine, still.
Thankfully, v2.4.1 was released recently, and flashing it from the Web UI magically revived my miner. So, be warned.
Bonus: File Hashes
For convenience, these are the SHA256 hashes of the files I used in this article: ``` da24fceb246f3b8b4dd94e5143f17bd38e46e5285e807ebd51627cb08f665c0a ESP-Miner-v2.4.1/esp-miner.bin 16c5c671391f0e3e88a3e79ce33fad3b0ec232b8572fad5e1e0d1ad3251ab394 ESP-Miner-v2.4.1/www.bin
d5182a15b6fa21d7b9b31bff2026d30afed9d769781a48db914730a5751e20c6 esp-miner-factory-205-v2.1.8.bin ```
-
 @ b8851a06:9b120ba1
2025-01-13 23:12:14
@ b8851a06:9b120ba1
2025-01-13 23:12:14In a world where sovereignty is supposedly sacred, a startling truth emerges: The United States' attempt to purchase Greenland has exposed how territories and their populations can still be viewed as tradeable assets in the 21st century. This investigation reveals the true scope of what could be the most audacious territorial acquisition since the Alaska Purchase of 1867.
THE SOVEREIGNTY PARADOX
When Danish Prime Minister Frederiksen declared "Greenland is not for sale," she inadvertently highlighted a crucial irony: Denmark's authority to reject the sale implies ownership of a territory seeking self-determination. Prime Minister Egede's recent accusation of Danish genocide over the 1960s forced contraceptive program adds a chilling historical context to this modern power play.
THE REAL PRICE OF A NATION
The initial estimates of $12.5-77 billion, calculated by former New York Fed economist David Barker, barely scratch the surface. The true cost approaches $2 trillion when factoring in: - Infrastructure development: $1.5 trillion - Annual subsidies: $775 million - Resident compensation: $5.7-57 billion - Environmental protection costs: Billions annually
THE COLONIAL ECHO CHAMBER
HISTORICAL WOUNDS AND MODERN AMBITIONS Trump's refusal to rule out military force against a NATO ally marks an unprecedented threat in post-WW2 diplomacy. Meanwhile, Donald #Trump Jr.'s "private visits" to Greenland, coupled with Denmark's pointed refusal to meet him, reveals the intersection of personal business interests and national security policy.
THE RESOURCE SOVEREIGNTY EQUATION
Beneath Greenland's ice lies an estimated $1.1 trillion in mineral wealth, presenting an alluring economic incentive. However, this potential wealth raises fundamental questions about resource sovereignty:
DEVELOPMENT COSTS - 24 major development projects needed - $5 billion per project - 25-year implementation timeline - Current GDP: $3.236 billion
STRATEGIC RESOURCES - Rare earth elements crucial for technology - 31.9 billion barrels of oil equivalent - Vast hydroelectric potential - Green hydrogen production possibilities
THE ENVIRONMENTAL STAKES
Greenland's ice sheet contains enough water to raise global sea levels by 23 feet. Climate change is rapidly transforming resource accessibility, while environmental protection costs would run into billions annually. This environmental transformation creates both opportunities and responsibilities:
- Tourism sector potential: $450 million annually
- Climate change monitoring costs
- Environmental protection infrastructure
- Indigenous land management rights
THE GEOPOLITICAL CHESSBOARD
POWER DYNAMICS The acquisition would fundamentally alter Arctic power structures: - #NATO alliance relationships - Chinese economic interests - Arctic Council voting power - Maritime shipping routes
THE CHINESE SHADOW Denmark's 2017 intervention blocking Chinese acquisition of a former military base reveals Greenland's role in a larger geopolitical game. China's growing Arctic ambitions add urgency to American interests.
THE MONARCHICAL DIMENSION
King Frederik X's strategic modification of #Denmark 's royal coat of arms to emphasize Greenland ownership serves as a direct challenge to American ambitions, adding traditional power structures to modern sovereignty disputes.
PROBABILITY AND RESISTANCE
Current analysis suggests: - 60% chance of failure due to international opposition - 30% chance of diplomatic compromise - 10% chance of successful acquisition
THE INFLATION FACTOR
The purchase would trigger significant inflationary pressures through: - Massive fiscal expenditure in an already heated economy - Supply chain disruptions - Construction and development costs - Core PCE inflation impact - Federal Reserve policy complications
LEGAL AND FINANCIAL HURDLES
The acquisition faces numerous obstacles: - International maritime law complications - Indigenous rights considerations - Existing mining licenses - Danish sovereign debt obligations - NATO alliance implications
THE SOVEREIGNTY SOLUTION
The path forward likely lies not in purchase but in supporting Greenlandic self-determination. With only 56,000 residents, the per capita acquisition cost would be astronomical, but the human cost of ignoring sovereignty rights would be immeasurable.
CONCLUSION: THE PRICE OF FREEDOM
The true cost of purchasing Greenland extends beyond economics into the realm of human rights and dignity. As climate change transforms the Arctic landscape, the question isn't whether Greenland can be bought—it's whether territorial transactions should have any place in a world that claims to value self-determination.
The convergence of colonial history, indigenous rights, and geopolitical ambitions in Greenland serves as a mirror to our times. While major powers still think in terms of territorial acquisition, the people of Greenland remind us that sovereignty isn't for sale. Their struggle for self-determination, caught between American ambitions, Chinese influence, Danish sovereignty, and their own independence aspirations, may well define the future of Arctic politics and indigenous rights in the 21st century.
The most viable path appears to be enhanced economic partnership without formal territorial acquisition, possibly through a free association agreement following #Greenland 's potential independence. As the Arctic's strategic importance grows, this #nostr analysis becomes increasingly relevant for future policy considerations and global power dynamics.
-
 @ 16d11430:61640947
2025-01-21 12:21:41
@ 16d11430:61640947
2025-01-21 12:21:41Hark, yon travellers, and gather round, for I shall tell thee a tale most grievous and yet queer, of the Black Knights of Sydney and their wretched deeds. In the land where the sun doth ever blaze and the sand kisseth the seas at Manly and Bondi alike, there rose a brood of shadowy lords, clad not in chain nor plate, but in ill-gotten power and tongues oiled with guile. These knights, though mighty in posture, were naught but fraudsters, lording o’er their glass castles with tools of torment and tormentors loyal yet weary.
The Black Knights and Their Tools of Torture
In their domains of steel and enchantment, the Black Knights kept the lower folk—Outsiders and plebs alike—beneath their boots, using tools most cruel. Chief amongst these instruments was the Rack of Review, a devilish device to which all Outsiders were summoned come every quarter moon. Here, the Knights would scry their scrolls of "metrics" and "outputs," their eyes narrowing as they spoke vile proclamations:
"Thy deliverables are tardy, thy productivity meagre, and thy enthusiasm fit for the dunghill!"
Strapped metaphorically to the Rack, the poor sods would be stretched—not in limb but in labour, their hours extended without mercy, until naught but a husk remained.
The Gantt Wheel of Doom
Lo, there was also the Gantt Wheel, a terrible, spinning contraption upon which the timelines of the kingdom were writ. The Wheel turned ever faster as the Knights demanded projects be completed "on the morrow" or "ere the next new moon." The Outsiders, desperate to keep pace, toiled day and night, only to find their efforts scoffed at and their souls ground into dust beneath the Wheel’s ceaseless spin.
The Slack Shackles
But even in their rare moments of respite, the Outsiders were bound by the Slack Shackles, cursed chains that buzzed and hummed without end. Messages did flow through these infernal devices, demanding updates, meetings, and “quick chats” at all hours. Ne’er a dawn nor dusk passed without the Shackles tightening their grip, leaving their victims weary and witless.
The Documentation Dungeon
When a fresh Outsider entered the kingdom, they were hurled into the dreaded Documentation Dungeon, a chaotic cavern where ancient scrolls lay piled high, each more incomprehensible than the last. “Figure it out!” barked the Trusty Squires, those harried managers who served the Knights with reluctant fervour. And so the Outsiders wandered the Dungeon’s depths, driven mad by its riddles, while the Squires hurried off to tend to their younglings or steal a quiet moment of peace.
The Outsiders’ Plight
Amongst the many Outsiders was one of particular ambition, newly arrived from lands far beyond the kingdom. Full of ideas and burning with determination, this Outsider sought not merely survival, but to reshape the very kingdom itself. Yet their brilliance was met with scorn, their ideas brushed aside by the Squires, whose refrain was always the same:
"Aye, 'tis a good idea, but I’ve no time for thee."
The Black Knights, meanwhile, saw in the Outsider not potential, but peril. "This one dares to shine too brightly," they muttered. "We must see them humbled."
The Reckoning
It came to pass that the Outsider, weary of the endless grind, began to see the cracks in the Knights’ armour. They discovered that the Rack’s metrics were flawed, the Gantt Wheel’s spin could be slowed, and the Slack Shackles could be hacked. Sharing their findings with their fellow Outsiders, they sowed the seeds of rebellion.
The Trusty Squires, long burdened by their double lives as enforcers and reluctant parents, began to waver. "Perhaps," they whispered, "the Outsiders speak true." And so, one by one, the Squires laid down their scrolls and joined the cause.
When the day of reckoning came, the Outsiders and their allies turned the Knights’ tools against them. The Rack, once a symbol of shame, now displayed the Knights’ own failings for all to see. The Gantt Wheel ground to a halt, and the Slack Shackles shattered into silence.
The Knights, their power undone, fled to their glass castles, clutching at their dwindling authority. The Outsiders, meanwhile, seized the kingdom, dismantling the tools of oppression and forging a new order where all could thrive.
A New Order
And so it was that the land of Sydney was reborn, no longer ruled by the Black Knights, but by a council of equals. The Rack was transformed into a table of collaboration, the Gantt Wheel into a tool of fairness, and the Shackles into oaths of trust. The Documentation Dungeon was cleared and made into a grand library, where knowledge was shared freely.
As for the Black Knights, their names faded from memory, their castles left to crumble. And the Outsiders, once strangers in a strange land, became the stewards of a kingdom built not on fear, but on hope.
And lo, the folk of Sydney lived happily, though ever wary of the shadows where new knights might rise. For they had learned a hard truth: that tyranny doth thrive where ambition goes unguarded, and freedom must ever be defended, even on the golden shores of Manly.
-
 @ b17fccdf:b7211155
2025-01-21 17:29:54
@ b17fccdf:b7211155
2025-01-21 17:29:54Some sections inside of the guide:
- Set up Dynamic DNS
- Wireguard VPN server & client side configurations
- Install & configure the WireGuard VPN Client on a mobile phone
- Configure additional servers & clients
- Use your router’s DDNS preconfigured provider
- Port forwarding on NAT/PAT router
Link to the bonus guide HERE
Enjoy it MiniBolter! 💙
-
 @ 812cff5a:5c40aeeb
2025-01-13 16:07:25
@ 812cff5a:5c40aeeb
2025-01-13 16:07:25نوستر الآن
كل تطبيقات نوستر حاليا هي مجرد عميل يتواصل مع مجموعة سيرڤرات متفرقة، نوتديك مختلف كليا
اذا كنت مستخدم لنوستر فانت على الاغبل تعلم ان الطريقة التي نتواصل من خلالها مع البروتوكول هي من خلال تطبيقات تتواصل مع سيرفرات مختلفة (تعرف باسم ريلاي) لارسال واستقبال المنشورات المتنوعة المتعارف عليها في البروتوكول.
حتى الان اغلب هذه التطبيقات تتواصل تشكل مباشر مع السيرڤرات، وبصورى عامة هي تؤدي وظيفة محدودة.
يمكن تشبيه هذه المرحلة من نوستر بزمن التطبيقات قبل انظمة التشغيل.
نوستر قريباً
نوتديك هو اشبه بنظام تشغيل لتطوير جميع انواع التطبيقات بدل من ان يكون تطبيق نوستر محدود الميزات
يعمل نوتديك كطبقة ما بين السيرفرات والتطبيقات. يحتوي نوتديك على سيرڤر داخلي يتواصل مع السيرڤرات الاخرى ويقوم باستلام تحديثات الشبكة بشكل دائم. اما المستخدم، فيتفاعل مع نوتديك والسيرڤر المحلي فقط. هذا يسمح للمستخدم في التعامل مع نوتديك حتى لو لم يكن مرتبط بالانترنت، كما ان التواصل سريع جدا من منظور السمتخدم.
امكانيات لا محدودة
اي مطور بامكانه استخدام الخدمات التي يقدمها نوتديك لتطوير تطبيقات تعمل داخل نوتديك وتستفيد من سرعة السيرڤر الداخلي
الجميل في عالم الكود المفتوح ان المطورين يقومون بتبني الافكار الجيدة والبدء بالبناء عليها بشكل فوري وبدوم قيود الموافقات والبيروقراطية العقيمة الموجودى في الشركات الكبيرة. بدأنا اللآن من رؤية التطبيقات المتوافقة مع نوتديك تظهر. اول مثال هو تطبيق زاب دوت سريم للبث المباشر. وهذه مجرد البداية، تقنياً، اي تطبيق على نوستر يستطيق الاستفادة من هذه الميزات.

كيف تستخدم نوتديك؟
نوتديك مازال في ايامه الأولى، لكن اذا كنت من مستخدمين داموس البتنفسجي أو لديك بعض الخبرة التقنية فيمكن تحميله من موقع github
اذا كنت من مشتركي داموس البنفسجي، يمكنك تحميل نوتديك من هذا الرابط: notedeck
اذا اردت استخدام آخر تحديق من نوتديك عليك تحميل لغة برمجة rust بالإضافة إلى بعض تطبيقات الكومبايلنغ ثم تشغيل التطبيق من هذا الرابط: github-notedeck
للمساعدة
اذا احتجتم لمساعدة أو ترغبون في تقديم الدعم في تطوير نوتديك، يمكنكم التواصل مع nostr:npub1nje4ghpkjsxe5thcd4gdt3agl2usxyxv3xxyx39ul3xgytl5009q87l02j
للتواصل مع المطور: nostr:npub1xtscya34g58tk0z605fvr788k263gsu6cy9x0mhnm87echrgufzsevkk5s
-
 @ a95c6243:d345522c
2025-01-13 10:09:57
@ a95c6243:d345522c
2025-01-13 10:09:57Ich begann, Social Media aufzubauen, \ um den Menschen eine Stimme zu geben. \ Mark Zuckerberg
Sind euch auch die Tränen gekommen, als ihr Mark Zuckerbergs Wendehals-Deklaration bezüglich der Meinungsfreiheit auf seinen Portalen gehört habt? Rührend, oder? Während er früher die offensichtliche Zensur leugnete und später die Regierung Biden dafür verantwortlich machte, will er nun angeblich «die Zensur auf unseren Plattformen drastisch reduzieren».
«Purer Opportunismus» ob des anstehenden Regierungswechsels wäre als Klassifizierung viel zu kurz gegriffen. Der jetzige Schachzug des Meta-Chefs ist genauso Teil einer kühl kalkulierten Business-Strategie, wie es die 180 Grad umgekehrte Praxis vorher war. Social Media sind ein höchst lukratives Geschäft. Hinzu kommt vielleicht noch ein bisschen verkorkstes Ego, weil derartig viel Einfluss und Geld sicher auch auf die Psyche schlagen. Verständlich.
«Es ist an der Zeit, zu unseren Wurzeln der freien Meinungsäußerung auf Facebook und Instagram zurückzukehren. Ich begann, Social Media aufzubauen, um den Menschen eine Stimme zu geben», sagte Zuckerberg.
Welche Wurzeln? Hat der Mann vergessen, dass er von der Überwachung, dem Ausspionieren und dem Ausverkauf sämtlicher Daten und digitaler Spuren sowie der Manipulation seiner «Kunden» lebt? Das ist knallharter Kommerz, nichts anderes. Um freie Meinungsäußerung geht es bei diesem Geschäft ganz sicher nicht, und das war auch noch nie so. Die Wurzeln von Facebook liegen in einem Projekt des US-Militärs mit dem Namen «LifeLog». Dessen Ziel war es, «ein digitales Protokoll vom Leben eines Menschen zu erstellen».
Der Richtungswechsel kommt allerdings nicht überraschend. Schon Anfang Dezember hatte Meta-Präsident Nick Clegg von «zu hoher Fehlerquote bei der Moderation» von Inhalten gesprochen. Bei der Gelegenheit erwähnte er auch, dass Mark sehr daran interessiert sei, eine aktive Rolle in den Debatten über eine amerikanische Führungsrolle im technologischen Bereich zu spielen.
Während Milliardärskollege und Big Tech-Konkurrent Elon Musk bereits seinen Posten in der kommenden Trump-Regierung in Aussicht hat, möchte Zuckerberg also nicht nur seine Haut retten – Trump hatte ihn einmal einen «Feind des Volkes» genannt und ihm lebenslange Haft angedroht –, sondern am liebsten auch mitspielen. KI-Berater ist wohl die gewünschte Funktion, wie man nach einem Treffen Trump-Zuckerberg hörte. An seine Verhaftung dachte vermutlich auch ein weiterer Multimilliardär mit eigener Social Media-Plattform, Pavel Durov, als er Zuckerberg jetzt kritisierte und gleichzeitig warnte.
Politik und Systemmedien drehen jedenfalls durch – was zu viel ist, ist zu viel. Etwas weniger Zensur und mehr Meinungsfreiheit würden die Freiheit der Bürger schwächen und seien potenziell vernichtend für die Menschenrechte. Zuckerberg setze mit dem neuen Kurs die Demokratie aufs Spiel, das sei eine «Einladung zum nächsten Völkermord», ernsthaft. Die Frage sei, ob sich die EU gegen Musk und Zuckerberg behaupten könne, Brüssel müsse jedenfalls hart durchgreifen.
Auch um die Faktenchecker macht man sich Sorgen. Für die deutsche Nachrichtenagentur dpa und die «Experten» von Correctiv, die (noch) Partner für Fact-Checking-Aktivitäten von Facebook sind, sei das ein «lukratives Geschäftsmodell». Aber möglicherweise werden die Inhalte ohne diese vermeintlichen Korrektoren ja sogar besser. Anders als Meta wollen jedoch Scholz, Faeser und die Tagesschau keine Fehler zugeben und zum Beispiel Correctiv-Falschaussagen einräumen.
Bei derlei dramatischen Befürchtungen wundert es nicht, dass der öffentliche Plausch auf X zwischen Elon Musk und AfD-Chefin Alice Weidel von 150 EU-Beamten überwacht wurde, falls es irgendwelche Rechtsverstöße geben sollte, die man ihnen ankreiden könnte. Auch der Deutsche Bundestag war wachsam. Gefunden haben dürften sie nichts. Das Ganze war eher eine Show, viel Wind wurde gemacht, aber letztlich gab es nichts als heiße Luft.
Das Anbiedern bei Donald Trump ist indes gerade in Mode. Die Weltgesundheitsorganisation (WHO) tut das auch, denn sie fürchtet um Spenden von über einer Milliarde Dollar. Eventuell könnte ja Elon Musk auch hier künftig aushelfen und der Organisation sowie deren größtem privaten Förderer, Bill Gates, etwas unter die Arme greifen. Nachdem Musks KI-Projekt xAI kürzlich von BlackRock & Co. sechs Milliarden eingestrichen hat, geht da vielleicht etwas.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ fd208ee8:0fd927c1
2025-01-19 12:10:10
@ fd208ee8:0fd927c1
2025-01-19 12:10:10I am so tired of people trying to waste my time with Nostrized imitations of stuff that already exists.
Instagram, but make it Nostr. Twitter, but make it Nostr. GitHub, but make it Nostr. Facebook, but make it Nostr. Wordpress, but make it Nostr. GoodReads, but make it Nostr. TikTok, but make it Nostr.
That stuff already exists, and it wasn't that great the first time around, either. Build something better than that stuff, that can only be brought into existence because of Nostr.
Build something that does something completely and awesomely new. Knock my socks off, bro.
Cuz, ain't nobody got time for that.
-
 @ e0921d61:e0fe7bd5
2025-01-13 06:22:15
@ e0921d61:e0fe7bd5
2025-01-13 06:22:15My reading list for 2025 consists of 15 books in 4 categories
- Islam
- Economics
- Civilization/History
- And René Guénon gets his own category 😂
Economics list:
- Epistemological Problems of Economics by Ludwig von Mises
The title seems intriguing and I've been meaning to read this for a while. My favorite chapter in human action is the one where Mises talks about the epistemological problems, so I'm hoping he expands on it here.
- Abundance, Generosity, and the State: An Inquiry into Economic Principles by Jörg Guido Hülsmann
This is from the same author that wrote one of my all time favorite "Bitcoin book", the Ethics of Money Production. This one explores charity from the Austrian perspective, and there's a really good podcast episode that Steophan Livera did with Hülsmann about this book.
- The Economics and Ethics of Private Property: Studies in Political Economy and Philosophy by Hans-Hermann Hoppe
I'm planning to read every Hoppe book, so this one had to go on the list.
- Why Minsky Matters: An Introduction to the Work of a Maverick Economist by L. Randall Wray
I've been meaning to read this for a while now, it was recommend to me by Ibn Maghrebi (nostr:npub1chmhgx9nwxdpwv6jj6qs257fwzrhtsjh2egvyvqq3rmzfy8cd5fq4nr4y5). Looks interesting and I wonder how similar Minsky's views are compared to Austrian Economics.
Islam list
- Reforming Modernity: Ethics and the New Human in the Philosophy of Abdurrahman Taha by Wael Hallaq
I want to read more Hallaq since reading the Impossible State, and this seems like something I'd enjoy, and it supposedly helps bring more context for the next book in this list.
- God's property: Islam, Charity, and the Modern State by Nada Moumtaz
I've had this book in my reading list for a while. The history of charity in Islamic civilizations is a fascinating topic to me.
- Islam between East and West 'Aiija 'Ali Izetbegovic
I actually don't know anything about this book other than seeing many folks on MT reference it a lot. Seems like something I must read.
- The Reconstruction of Religious Thought in Islam by Muhammad Iqbal
Got this one off the SAIF reading list.
Civilization/History List
- Energy and Civilization: A History by Vaclav Smil
Seems like an interesting book about energy
- Dirt: The Erosion of Civilizations by David R. Montgomery
I've had this on my reading list for a while, and I find the subject of soil to be fascinating. Seems interesting.
- The Muqaddimah: An Introduction to History by Ibn Khaldun
I'm ashamed to admit that I still haven't read this book. It's referenced a lot in other books talking about history and civilization. It's time for me to read this.
- The Time of the Bedouin: on the Politics of power by Ian Dallas
Ian Dallas is Shaykh Abdalqadir As-Sufi, and I want to read more of his works, as he understood the scope and nature of the Riba money problem long before I was even born!
René Guénon list
I've been meaning to read Guénon for a while now, and I don't know much about his philosophy but I've liked the few quotes I've read on certain Twitter threads. I'm very interested in how he approaches criticizing modernity.
- East and West
- The Crisis of the Modern World

- The Reign of Quantity & the Signs of the Times
And that's it. I'm hopeful I can get through all 15 books this year inshaAllah.
-
 @ 16d11430:61640947
2025-01-21 09:07:27
@ 16d11430:61640947
2025-01-21 09:07:27In the modern world, human existence often feels like a series of transactions. Our labor, emotions, and even our identities are bought, sold, and traded in systems that shape how we live and think. From the workplace to the digital economy, commodification—the transformation of people and their qualities into marketable goods—is a driving force. To explore this, we can draw a provocative yet insightful parallel between corporations, brothels, and the psychological toll of commodifying the self.
The Nature of Commodification
Commodification begins when something intrinsic, like human labor, creativity, or even intimacy, is turned into a product to be exchanged. This process is not inherently negative; it has enabled trade, specialization, and economies of scale. However, when commodification extends to the very essence of human life, it can distort how we view ourselves and others.
In corporations, employees are reduced to "human resources," evaluated for their productivity and cost-effectiveness.
In brothels, intimacy—a deeply personal and emotional act—is transformed into a service exchanged for money.
Both systems, while different in form and function, rely on similar transactional mechanics that highlight the tension between value creation and value extraction.
The Psychological Impact of Transactional Systems
When humans are commodified, a subtle but profound psychological shift occurs. The person begins to see themselves and others as products or tools, rather than as complex, multifaceted beings. This can lead to:
- Alienation from the Self
In corporations, workers may feel disconnected from the fruits of their labor, performing tasks that serve abstract goals (like shareholder profits) rather than personal or communal fulfillment.
In brothels, commodifying intimacy can create a dissonance between personal emotions and professional detachment.
- Reductionism in Identity
Both systems reduce individuals to specific roles: the "employee" or the "service provider." This narrow definition can strip away the richer dimensions of identity, leading to feelings of inadequacy or loss of purpose.
The language used—whether "key performance indicators" in corporations or "clients and services" in brothels—reinforces this reductionism.
- Emotional Transactionalism
When human relationships are repeatedly framed in transactional terms, individuals may struggle to form connections based on trust and reciprocity. Instead, they might view all interactions as exchanges of value, weakening the bonds of empathy and community.
Corporations and Brothels: Ethical and Unethical Dimensions
To fully understand the parallels, it’s important to acknowledge the spectrum of ethical possibilities within these systems. Both corporations and brothels can operate in ways that empower or exploit, depending on their structure, governance, and priorities.
Exploitation: When Systems Extract Value
In corporations, employees may feel like cogs in a machine, with minimal control over their work or compensation. Performance metrics, layoffs, and rigid hierarchies often amplify feelings of disposability.
In brothels, particularly those in unregulated or exploitative settings, workers may experience coercion, unsafe conditions, and a lack of autonomy over their lives.
Empowerment: When Systems Create Value
Ethical corporations foster creativity, collaboration, and meaningful contributions, treating employees as partners in a shared mission rather than mere labor inputs.
Progressive brothels, when regulated and consensual, can provide safe spaces for individuals to exercise autonomy, set boundaries, and earn a livelihood on their terms.
The key distinction lies in the balance between value creation and extraction, agency and coercion, empowerment and exploitation.
The Bitcoin Perspective: A Model for Fair Systems
Bitcoin offers a lens through which to critique commodification and envision systems that respect human agency and dignity. Unlike traditional corporations or centralized institutions, Bitcoin operates as a decentralized, transparent network where value is exchanged without middlemen or coercion. Its principles of proof of work, immutability, and voluntary participation provide a counterpoint to the exploitative tendencies of fiat systems.
- Transparency and Accountability
In Bitcoin, every transaction is recorded on a public ledger, ensuring that no entity can obscure or manipulate value flows.
Similarly, corporations and brothels could adopt transparent governance models, where stakeholders—whether workers, customers, or clients—can verify fairness and accountability.
- Agency and Sovereignty
Bitcoin restores financial control to individuals, allowing them to participate in the economy on their terms.
Ethical corporations and brothels should likewise empower individuals with choices and the ability to set their terms of participation.
- Value Without Exploitation
Bitcoin’s decentralized system eliminates the need for exploitative intermediaries. Applying this principle, organizations could prioritize equitable value exchange, ensuring that no one is reduced to a disposable asset.
Healing the Psychological Impact
To move beyond the psychological toll of commodification, societies must reimagine systems of work and exchange. This involves:
- Redefining Value
Value should extend beyond monetary metrics to include well-being, relationships, and personal growth. Organizations must recognize that human worth cannot be quantified.
- Restoring Meaning
Work and services, whether in corporations or brothels, should align with personal values and societal benefits. This creates a sense of purpose and connection.
- Fostering Empathy
Recognizing the humanity of everyone involved in a system—whether coworkers, clients, or customers—helps rebuild trust and compassion.
Conclusion: A New Paradigm for Transactional Systems
The metaphor of corporations as brothels is not about judgment but about understanding how transactional systems shape our psychology and relationships. By examining these parallels, we can challenge the commodification of the self and advocate for systems that prioritize human dignity, agency, and fairness.
Bitcoin, as a decentralized, transparent alternative, offers a glimpse of what such systems could look like. It challenges us to move beyond extraction and exploitation, toward value exchange that respects the complexity of human life. In doing so, it invites us to create a world where transactions do not diminish us but empower us to live fully and authentically.
-
 @ b17fccdf:b7211155
2025-01-21 17:07:47
@ b17fccdf:b7211155
2025-01-21 17:07:47 -
 @ 6871d8df:4a9396c1
2025-01-18 20:12:46
@ 6871d8df:4a9396c1
2025-01-18 20:12:46## 2024 Prediction Reflections
Politics
Democrats & 2024 Election
- “Democrats’ attempt to stifle democracy will likely put Trump in the White House. If not, some real sketchy stuff would need to happen to keep him out.”
This prediction was exactly right. The assassination attempt on Trump seemed to be the final blow for the Democrats. Despite a heavy push my legacy media, Trump won handily.
The Democrats switched to Kamala Harris after Biden showed signs of incapacity, most notably in the first debate against Trump.
My prediction for the election also turned out to be exactly right, which, thank you Robert Barnes and Richard Baris.
Evidence of Institutional Ideological Capture
- “People will continue to wake up to ideologically captured institutions, and DEI will be the main loser.”
Trump’s resounding election victory underscores that the public is increasingly aware of (and rejecting) such institutional capture.
Of note, Boeing comes to mind as an institution that had a tough time in 2024, in large part to DEI. Nothing seemed to function correctly. The biggest story being how they stranded people in space
Media & Public Opinion
Rise of Independent & Alternative Media
- “Independent and alternative media will continue to grow as people’s trust in legacy media declines.”
Twitter (X), under Elon Musk, shattered mainstream media’s influence far more than expected. As Elon has said, “You are the media now.” Alternative sources are king. - Notable Example: Kamala Harris’s decision not to appear on the Joe Rogan podcast contrasted with Trump’s appearance, further highlighting the power shift to alternative media.
Markets & IPOs
Interest Rates & Public Markets
- “As interest rates come down, I expect public markets and IPOs to heat up.”
This did not play out. Companies that were expected to go public in 2024 remain private in 2025. The reasons are varied, but there is confidence that 2025 might see changes.
Technology & AI
LLMs & AI Adoption
- “AI and LLMs will continue to move at a rapid rate, increasing productivity. Tools like Bard will become more mainstream.”
AI did take off. Usage among nontechnical users increased, and it’s no longer uncommon for people to default to AI-driven tools rather than Google search.
Decentralized AI
- “I hope to see a rise in decentralized AI to counter big-player LLMs.”
We didn’t see explicit ‘decentralized AI’ breakthroughs, but more players entered the AI market. ChatGPT still dominates, with Elon’s ‘Grok’ making moves. Google, Meta, and Microsoft remain active but slightly behind in usage.
Bitcoin & Digital Assets
Institutional Adoption of Bitcoin
- “2024 will bring more institutions to Bitcoin. Possibly another large company or nation-state. The ETF should help, likely pushing BTC to a new all-time high.”
No large public company or nation-state placed a bet, but smaller public companies did. Michael Saylor presented to Microsoft’s Board, which was the closest instance to a major move.
- Price Movement: Bitcoin did hit a new all-time high, rising to as much as $108k in 2024.Lightning Network
- “Lightning will improve but remain primarily used for acquiring Bitcoin, not everyday payments.”
Still true. Lightning usage remains tiny relative to broader Bitcoin adoption.
Nostr Adoption
- “Nostr will grow, and we’ll see new companies leverage this network beyond just social media.”
Growth continues, but Elon Musk’s Twitter takeover slowed adoption. Nostr will remain niche until a major catalyst occurs (e.g., a big player joins or forced usage due to censorship).
Stablecoin-Specific Regulations
- “Expect stablecoin regulations in 2024 that’ll be favorable to them.”
This didn’t happen, largely due to the administration’s hostility. Expect potential change in 2025.
Miscellaneous 2024 Reflections
- Return to Sanity
- 2024 felt like sanity prevailed, largely due to the Democrats’ collapse behind Biden and Harris and Elon’s Twitter dominance.
- Operation Chokepoint 2.0
- Received a lot of attention, and I’m thankful it did because my experience at Strike was radicalizing and extreme.
- Bryan Johnson & Anti-Aging
- He burst onto the scene with his obsession over biomarkers. I see it as misguided—chasing markers in isolation doesn’t automatically yield a healthy system.
- Apple’s Rough Year
- Without a visionary leader, Apple appears to be scraping by on existing products rather than innovating.
- Google Under Fire
- Google is in a tough fight with the government, just as it seems they’re on their heels with AI competition.
2025 Predictions
-
Bitcoin’s Performance Bitcoin will have a good year, but not better than 2024. To beat 2024, it must close above 206k on December 31, 2025. I’ll take the under on that.
- I am not ruling out it to be over that at some point in 2025.
-
Twitter’s Success Continues to Stunt nostr
- Nostr adoption will stay slow due to Elon’s dominant influence with X (Twitter).
- As long as it remains a beacon of free speech, I doubt we see an exodus.
-
Rumble integrating Tether might help if they allow Nostr-like features (zaps), but that seems unlikely.
-
Apple
-
Apple will continue its rent-seeking behavior and put out underwhelming products.
-
Google’s Quantum & AI
- Recent buzz about Google’s quantum chip and AI improvements won’t pan out as a big deal.
-
Google will continue to trail OpenAI and xAI in practical LLM usage.
-
Elon, Vivek & DOGE
-
I expect them to deliver more than critics think. They’ll expose bloat and inefficiencies in ways that will shake up norms. I greatly welcome this. I wouldn’t bet against them.
-
Mainstream Media Reckoning
- In Trump’s second term, mainstream news outlets will face a real reckoning, as I can’t see how their bias can continue.
- They’ll have to reduce their bias or risk bankruptcy.
-
Alternative media’s growth trend continues, especially as Twitter keeps exposing mainstream outlets’ weaknesses.
-
RFK Delivers
-
We will see big changes in the health space due to RFK at HHS. These are changes that I am very excited to see.
-
Foreign Policy
- With the transition to Trump, I expect some foreign policy wins that will buck the establishment but will deliver wins that are not thought possible by the “experts.”
Closing Note
- Overall 2024: It was a year of major political upheaval, vindication for Bitcoin, and continued AI advances.
- Outlook for 2025: Bitcoin remains strong, AI competition heats up, and media institutions face existential challenges. I’m optimistic for continued decentralization and a more level playing field across tech, finance, and politics. I think the start of Trump’s second term will be very strong for the market, health, and culture. Accelerate.
-
 @ 6f3670d9:03f04036
2024-12-29 06:51:25
@ 6f3670d9:03f04036
2024-12-29 06:51:25This is my first long-form post. The starting line.
There's nothing of value here. Just using this as a marker.
I hope to post a lot more. Documenting how I made something work would be very useful to me, and hopefully others, but I've been too lazy to do that. Wish me luck!
Stay humble,
dumb-package -
 @ b17fccdf:b7211155
2025-01-21 17:02:21
@ b17fccdf:b7211155
2025-01-21 17:02:21The past 26 August, Tor introduced officially a proof-of-work (PoW) defense for onion services designed to prioritize verified network traffic as a deterrent against denial of service (DoS) attacks.
~ > This feature at the moment, is deactivate by default, so you need to follow these steps to activate this on a MiniBolt node:
- Make sure you have the latest version of Tor installed, at the time of writing this post, which is v0.4.8.6. Check your current version by typing
tor --versionExample of expected output:
Tor version 0.4.8.6. This build of Tor is covered by the GNU General Public License (https://www.gnu.org/licenses/gpl-3.0.en.html) Tor is running on Linux with Libevent 2.1.12-stable, OpenSSL 3.0.9, Zlib 1.2.13, Liblzma 5.4.1, Libzstd N/A and Glibc 2.36 as libc. Tor compiled with GCC version 12.2.0~ > If you have v0.4.8.X, you are OK, if not, type
sudo apt update && sudo apt upgradeand confirm to update.- Basic PoW support can be checked by running this command:
tor --list-modulesExpected output:
relay: yes dirauth: yes dircache: yes pow: **yes**~ > If you have
pow: yes, you are OK- Now go to the torrc file of your MiniBolt and add the parameter to enable PoW for each hidden service added
sudo nano /etc/tor/torrcExample:
```
Hidden Service BTC RPC Explorer
HiddenServiceDir /var/lib/tor/hidden_service_btcrpcexplorer/ HiddenServiceVersion 3 HiddenServicePoWDefensesEnabled 1 HiddenServicePort 80 127.0.0.1:3002 ```
~ > Bitcoin Core and LND use the Tor control port to automatically create the hidden service, requiring no action from the user. We have submitted a feature request in the official GitHub repositories to explore the need for the integration of Tor's PoW defense into the automatic creation process of the hidden service. You can follow them at the following links:
- Bitcoin Core: https://github.com/lightningnetwork/lnd/issues/8002
- LND: https://github.com/bitcoin/bitcoin/issues/28499
More info:
- https://blog.torproject.org/introducing-proof-of-work-defense-for-onion-services/
- https://gitlab.torproject.org/tpo/onion-services/onion-support/-/wikis/Documentation/PoW-FAQ
Enjoy it MiniBolter! 💙
-
 @ a95c6243:d345522c
2025-01-03 20:26:47
@ a95c6243:d345522c
2025-01-03 20:26:47Was du bist hängt von drei Faktoren ab: \ Was du geerbt hast, \ was deine Umgebung aus dir machte \ und was du in freier Wahl \ aus deiner Umgebung und deinem Erbe gemacht hast. \ Aldous Huxley
Das brave Mitmachen und Mitlaufen in einem vorgegebenen, recht engen Rahmen ist gewiss nicht neu, hat aber gerade wieder mal Konjunktur. Dies kann man deutlich beobachten, eigentlich egal, in welchem gesellschaftlichen Bereich man sich umschaut. Individualität ist nur soweit angesagt, wie sie in ein bestimmtes Schema von «Diversität» passt, und Freiheit verkommt zur Worthülse – nicht erst durch ein gewisses Buch einer gewissen ehemaligen Regierungschefin.
Erklärungsansätze für solche Entwicklungen sind bekannt, und praktisch alle haben etwas mit Massenpsychologie zu tun. Der Herdentrieb, also der Trieb der Menschen, sich – zum Beispiel aus Unsicherheit oder Bequemlichkeit – lieber der Masse anzuschließen als selbstständig zu denken und zu handeln, ist einer der Erklärungsversuche. Andere drehen sich um Macht, Propaganda, Druck und Angst, also den gezielten Einsatz psychologischer Herrschaftsinstrumente.
Aber wollen die Menschen überhaupt Freiheit? Durch Gespräche im privaten Umfeld bin ich diesbezüglich in der letzten Zeit etwas skeptisch geworden. Um die Jahreswende philosophiert man ja gerne ein wenig über das Erlebte und über die Erwartungen für die Zukunft. Dabei hatte ich hin und wieder den Eindruck, die totalitären Anwandlungen unserer «Repräsentanten» kämen manchen Leuten gerade recht.
«Desinformation» ist so ein brisantes Thema. Davor müsse man die Menschen doch schützen, hörte ich. Jemand müsse doch zum Beispiel diese ganzen merkwürdigen Inhalte in den Social Media filtern – zur Ukraine, zum Klima, zu Gesundheitsthemen oder zur Migration. Viele wüssten ja gar nicht einzuschätzen, was richtig und was falsch ist, sie bräuchten eine Führung.
Freiheit bedingt Eigenverantwortung, ohne Zweifel. Eventuell ist es einigen tatsächlich zu anspruchsvoll, die Verantwortung für das eigene Tun und Lassen zu übernehmen. Oder die persönliche Freiheit wird nicht als ausreichend wertvolles Gut angesehen, um sich dafür anzustrengen. In dem Fall wäre die mangelnde Selbstbestimmung wohl das kleinere Übel. Allerdings fehlt dann gemäß Aldous Huxley ein Teil der Persönlichkeit. Letztlich ist natürlich alles eine Frage der Abwägung.
Sind viele Menschen möglicherweise schon so «eingenordet», dass freiheitliche Ambitionen gar nicht für eine ganze Gruppe, ein Kollektiv, verfolgt werden können? Solche Gedanken kamen mir auch, als ich mir kürzlich diverse Talks beim viertägigen Hacker-Kongress des Chaos Computer Clubs (38C3) anschaute. Ich war nicht nur überrascht, sondern reichlich erschreckt angesichts der in weiten Teilen mainstream-geformten Inhalte, mit denen ein dankbares Publikum beglückt wurde. Wo ich allgemein hellere Köpfe erwartet hatte, fand ich Konformismus und enthusiastisch untermauerte Narrative.
Gibt es vielleicht so etwas wie eine Herdenimmunität gegen Indoktrination? Ich denke, ja, zumindest eine gestärkte Widerstandsfähigkeit. Was wir brauchen, sind etwas gesunder Menschenverstand, offene Informationskanäle und der Mut, sich freier auch zwischen den Herden zu bewegen. Sie tun das bereits, aber sagen Sie es auch dieses Jahr ruhig weiter.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 16d11430:61640947
2025-01-21 08:17:01
@ 16d11430:61640947
2025-01-21 08:17:01Corporate infidelity—the betrayal of principles, trust, or ethics for personal or organizational gain—breeds a toxic "cheat culture" that often promotes cheaters to the highest ranks. This phenomenon undermines meritocracy, rewards unethical behavior, and creates a cycle where deception becomes normalized. Here's an exploration of how this happens, supported by evidence and psychoanalysis of the relationship between cheaters and corporate leadership.
- How Corporate Infidelity Breeds a Cheat Culture
Corporate infidelity sets a precedent that unethical behavior is acceptable if it delivers results. Over time, this shapes an organizational culture where:
-
Cheating Becomes a Norm: When employees see unethical practices rewarded or ignored, they learn that integrity is secondary to success.
-
Survival of the Craftiest: In such cultures, those who can manipulate systems, cut corners, or deceive stakeholders often rise faster than those adhering to principles.
-
Erosion of Accountability: A lack of accountability fosters a permissive environment, where leaders themselves engage in and benefit from unethical practices.
- Evidence of Cheat Culture in Leadership
Several high-profile scandals illustrate how cheating has propelled individuals to leadership positions:
Wells Fargo Fake Accounts Scandal
What Happened: Thousands of employees, pressured by unrealistic sales targets, created millions of unauthorized customer accounts.
Leadership's Role: Senior executives not only incentivized this behavior but ignored warnings from whistleblowers.
Outcome: The culture of cheating started at the top, as leaders prioritized growth over ethics, and they faced only minimal accountability initially.
Theranos and Elizabeth Holmes
What Happened: Elizabeth Holmes, the founder of Theranos, misrepresented the capabilities of her company’s blood-testing technology to investors and regulators.
Leadership Dynamics: Holmes created a culture where employees were pressured to meet impossible expectations, even if it meant falsifying results.
Outcome: Holmes’s rise was fueled by her charisma and ability to sell a dream, despite the underlying fraud.
Enron and Skilling’s Leadership
What Happened: Enron executives engaged in widespread accounting fraud to inflate profits and conceal debt.
Leadership’s Role: CEO Jeffrey Skilling cultivated a high-pressure environment that rewarded financial manipulation and punished transparency.
Outcome: Enron’s collapse highlighted how cheat culture at the top devastates entire organizations.
- Psychoanalysis: The Relationship Between Cheaters and Corporate Leadership
The relationship between cheaters and corporate leadership is symbiotic, driven by psychological and organizational factors:
A. Psychological Traits of Cheaters in Leadership
- Narcissism: Many corporate cheaters possess narcissistic traits, including an inflated sense of self-importance and a lack of empathy. They manipulate others to maintain their power and image.
Example: Elizabeth Holmes’s portrayal as a visionary leader allowed her to deflect scrutiny for years.
- Risk-Taking Behavior: Cheaters often thrive in environments where calculated risk-taking is rewarded, pushing boundaries until ethical lines are crossed.
Example: Enron executives’ risky financial strategies were initially celebrated as innovative.
- Machiavellianism: A tendency to prioritize personal gain over principles enables cheaters to navigate corporate politics and manipulate others.
Example: Executives at Volkswagen during the Dieselgate scandal prioritized market dominance over compliance.
B. Why Organizations Promote Cheaters
-
Results-Oriented Metrics: Companies often measure success by short-term outcomes (e.g., profits, growth) rather than long-term sustainability. Cheaters excel at delivering impressive metrics, even if through unethical means.
-
Fear and Obedience: Cheaters in leadership roles cultivate a culture of fear, discouraging dissent and ensuring compliance with their unethical practices.
-
Halo Effect: Charismatic cheaters, like Elizabeth Holmes or Jeffrey Skilling, use their charm and vision to distract from ethical shortcomings, earning trust from boards and investors.
-
Cultural Blind Spots: Organizations with weak ethical frameworks or poor governance fail to detect or address unethical behavior until it’s too late.
- The Long-Term Impact of Cheat Culture
The systemic promotion of cheaters to leadership has far-reaching consequences:
-
Erosion of Trust: Employees, investors, and customers lose faith in organizations when scandals come to light.
-
Demoralization of Ethical Employees: High-performing, ethical employees are often overlooked or pushed out, leading to talent attrition.
-
Reinforced Cycle of Corruption: When cheaters rise to power, they perpetuate a culture that rewards unethical behavior, creating a self-sustaining system.
-
Breaking the Cycle: Preventing Cheat Culture
-
Transparent Governance: Implementing decentralized systems like blockchain can provide immutable records of decisions and transactions, reducing opportunities for manipulation.
-
Ethical Leadership Training: Developing leaders with strong ethical foundations ensures accountability at the top.
-
Whistleblower Protections: Encouraging employees to report unethical practices without fear of retaliation can help identify and address issues early.
-
Focus on Long-Term Metrics: Shifting from short-term profits to long-term value creation reduces pressure to cheat.
-
Adopting Bitcoin Principles: Bitcoin’s trustless, decentralized nature eliminates reliance on charismatic but untrustworthy individuals, promoting accountability.
Conclusion
Corporate infidelity fosters a cheat culture where unethical behavior is rewarded and cheaters rise to the top. This dynamic is fueled by psychological traits like narcissism and organizational flaws such as results-oriented metrics and weak governance. High-profile scandals, from Theranos to Enron, illustrate the dangers of such cultures. However, with transparent systems, ethical leadership, and decentralized accountability mechanisms like Bitcoin, organizations can break this cycle and rebuild trust, integrity, and fairness in corporate leadership.
-
 @ 16d11430:61640947
2025-01-21 07:59:13
@ 16d11430:61640947
2025-01-21 07:59:13Corporate infidelity—marked by ethical breaches, dishonesty, and the prioritization of profits over principles—has plagued modern society. From environmental scandals to financial fraud, these betrayals erode trust, destabilize economies, and perpetuate inequality. However, the emergence of Bitcoin and its underlying blockchain technology presents a transformative solution. With its emphasis on transparency, decentralization, and immutability, Bitcoin offers a path to ending corporate infidelity and its widespread societal effects.
The Roots of Corporate Infidelity
Corporate infidelity thrives in centralized systems that lack accountability and incentivize short-term gains. Whether it's manipulating emissions data, exploiting customer trust, or undermining environmental stewardship, these actions are enabled by opaque structures, fiat-based incentives, and unchecked power.
Key Factors Enabling Corporate Infidelity:
-
Opaque Financial Systems: Fiat-based systems rely on centralized control, allowing manipulation, fraud, and mismanagement to go unchecked.
-
Short-Termism: Quarterly earnings reports and profit-driven motives often override long-term ethical commitments.
-
Lack of Transparency: Traditional corporate governance operates behind closed doors, making it difficult to identify and address misconduct.
-
Centralized Power: Concentrated authority within organizations enables unethical behavior to persist unchecked.
How Bitcoin and Blockchain Combat Corporate Infidelity
Bitcoin, as a decentralized, transparent, and immutable financial system, addresses the structural weaknesses that enable corporate infidelity. Here’s how:
- Immutable Transparency
Bitcoin’s blockchain is a public ledger where all transactions are permanently recorded and verifiable. This transparency makes it nearly impossible to manipulate financial data or hide unethical practices.
Impact on Corporate Governance: By integrating blockchain technology, companies can create verifiable records of financial transactions, supply chains, and decision-making processes, reducing opportunities for fraud and corruption.
- Decentralized Accountability
Bitcoin operates without central authority, redistributing power to a global network of participants. This decentralization reduces the risks of concentrated decision-making that often lead to unethical behavior.
Impact on Corporations: Decentralized systems empower stakeholders—employees, customers, and investors—to hold corporations accountable. Transparent decision-making eliminates the "black box" of traditional corporate governance.
- Alignment of Incentives
Bitcoin’s protocol incentivizes long-term participation and trust. Its deflationary nature discourages reckless monetary expansion, aligning with sustainable practices over speculative short-term gains.
Impact on Society: Corporations operating on Bitcoin-based systems are encouraged to prioritize stability and value creation, reducing the focus on quarterly profits at the expense of ethics.
- Smart Contracts and Automation
Blockchain-enabled smart contracts enforce agreements automatically without intermediaries. These contracts can ensure compliance with ethical and operational standards, removing the possibility of infidelity.
Example Use Case: Companies can automate ethical practices, such as verifying supply chain sustainability or ensuring fair wages, through immutable smart contracts.
- Trustless Systems
Bitcoin eliminates the need for trust in third parties by relying on cryptographic proof. This trustless design reduces opportunities for betrayal and infidelity within corporate structures.
Impact on Employees and Customers: With verifiable systems in place, stakeholders no longer need to rely on promises—they can verify outcomes independently.
Real-World Applications: Bitcoin in Action
- Supply Chain Transparency
Blockchain-based systems allow for end-to-end tracking of goods, ensuring ethical sourcing and eliminating fraud. Companies like IBM are already leveraging blockchain for supply chain transparency.
- Financial Integrity
Bitcoin eliminates the need for centralized banks and financial intermediaries, reducing risks of financial mismanagement. Companies can integrate Bitcoin payments to promote transparency in financial transactions.
- Decentralized Audits
Blockchain-based auditing ensures that financial reports are accurate and tamper-proof, making it harder for corporations to engage in fraudulent activities.
Transforming Society Through Bitcoin
The societal benefits of Bitcoin extend beyond the corporate world. By addressing corporate infidelity, Bitcoin can help create a more equitable, sustainable, and trustworthy society:
- Restoring Trust in Institutions
Bitcoin’s emphasis on transparency and accountability can rebuild public trust in corporations, governments, and financial systems.
- Promoting Ethical Leadership
Leaders operating in Bitcoin-based systems are incentivized to act ethically, as their actions are subject to public scrutiny.
- Reducing Inequality
By decentralizing power and removing intermediaries, Bitcoin empowers individuals and small businesses, reducing wealth concentration and systemic inequality.
- Accelerating Justice
Immutable records on the blockchain can expedite legal and regulatory processes, ensuring swift accountability for unethical behavior.
Challenges and the Road Ahead
While Bitcoin offers a powerful tool for combating corporate infidelity, its adoption faces challenges, including regulatory resistance, technical literacy gaps, and cultural inertia. To fully realize its potential:
-
Education and Advocacy: Stakeholders must understand Bitcoin’s capabilities and embrace its principles.
-
Policy Integration: Governments and organizations need to develop frameworks that encourage blockchain adoption.
-
Cultural Shift: A commitment to transparency, accountability, and decentralization must become a societal norm.
Conclusion
Corporate infidelity has long undermined trust, stability, and equality in society. Bitcoin offers a revolutionary alternative, providing the means and methods to end unethical practices through transparency, decentralization, and accountability. By embracing Bitcoin’s principles, corporations and societies can foster a future built on trust, integrity, and sustainable value creation—a future where betrayal of principles is no longer an option.
-
-
 @ dbb19ae0:c3f22d5a
2025-01-21 09:00:36
@ dbb19ae0:c3f22d5a
2025-01-21 09:00:36Warning: Use this at your own risk Backup your files before using them in the software Backup often, test your backup. Verify and dry test your files before doing a production run
I had to write this program because rmdir was claiming not to have enough authorization
context nostr:note1l0u4pw5xp73eultr9nf5tgmlsgnv9q05wdqha4t6grd4699v74zssshm40
```perl use strict; use warnings; use File::Path qw(remove_tree);
Specify the directory to be deleted
my $directory = 'c:\Users\mydirectory\mysubdirectory\';
Remove the directory
remove_tree($directory, {error => \my $err});
Check for errors
if (@$err) { foreach my $diag (@$err) { my ($file, $message) = %$diag; if ($file eq '') { print "General error: $message\n"; } else { print "Problem unlinking $file: $message\n"; } } } else { print "Directory successfully deleted.\n"; }
```
-
 @ eac63075:b4988b48
2024-11-09 17:57:27
@ eac63075:b4988b48
2024-11-09 17:57:27Based on a recent paper that included collaboration from renowned experts such as Lynn Alden, Steve Lee, and Ren Crypto Fish, we discuss in depth how Bitcoin's consensus is built, the main risks, and the complex dynamics of protocol upgrades.
Podcast https://www.fountain.fm/episode/wbjD6ntQuvX5u2G5BccC
Presentation https://gamma.app/docs/Analyzing-Bitcoin-Consensus-Risks-in-Protocol-Upgrades-p66axxjwaa37ksn
1. Introduction to Consensus in Bitcoin
Consensus in Bitcoin is the foundation that keeps the network secure and functional, allowing users worldwide to perform transactions in a decentralized manner without the need for intermediaries. Since its launch in 2009, Bitcoin is often described as an "immutable" system designed to resist changes, and it is precisely this resistance that ensures its security and stability.
The central idea behind consensus in Bitcoin is to create a set of acceptance rules for blocks and transactions, ensuring that all network participants agree on the transaction history. This prevents "double-spending," where the same bitcoin could be used in two simultaneous transactions, something that would compromise trust in the network.
Evolution of Consensus in Bitcoin
Over the years, consensus in Bitcoin has undergone several adaptations, and the way participants agree on changes remains a delicate process. Unlike traditional systems, where changes can be imposed from the top down, Bitcoin operates in a decentralized model where any significant change needs the support of various groups of stakeholders, including miners, developers, users, and large node operators.
Moreover, the update process is extremely cautious, as hasty changes can compromise the network's security. As a result, the philosophy of "don't fix what isn't broken" prevails, with improvements happening incrementally and only after broad consensus among those involved. This model can make progress seem slow but ensures that Bitcoin remains faithful to the principles of security and decentralization.
2. Technical Components of Consensus
Bitcoin's consensus is supported by a set of technical rules that determine what is considered a valid transaction and a valid block on the network. These technical aspects ensure that all nodes—the computers that participate in the Bitcoin network—agree on the current state of the blockchain. Below are the main technical components that form the basis of the consensus.
Validation of Blocks and Transactions
The validation of blocks and transactions is the central point of consensus in Bitcoin. A block is only considered valid if it meets certain criteria, such as maximum size, transaction structure, and the solving of the "Proof of Work" problem. The proof of work, required for a block to be included in the blockchain, is a computational process that ensures the block contains significant computational effort—protecting the network against manipulation attempts.
Transactions, in turn, need to follow specific input and output rules. Each transaction includes cryptographic signatures that prove the ownership of the bitcoins sent, as well as validation scripts that verify if the transaction conditions are met. This validation system is essential for network nodes to autonomously confirm that each transaction follows the rules.
Chain Selection
Another fundamental technical issue for Bitcoin's consensus is chain selection, which becomes especially important in cases where multiple versions of the blockchain coexist, such as after a network split (fork). To decide which chain is the "true" one and should be followed, the network adopts the criterion of the highest accumulated proof of work. In other words, the chain with the highest number of valid blocks, built with the greatest computational effort, is chosen by the network as the official one.
This criterion avoids permanent splits because it encourages all nodes to follow the same main chain, reinforcing consensus.
Soft Forks vs. Hard Forks
In the consensus process, protocol changes can happen in two ways: through soft forks or hard forks. These variations affect not only the protocol update but also the implications for network users:
-
Soft Forks: These are changes that are backward compatible. Only nodes that adopt the new update will follow the new rules, but old nodes will still recognize the blocks produced with these rules as valid. This compatibility makes soft forks a safer option for updates, as it minimizes the risk of network division.
-
Hard Forks: These are updates that are not backward compatible, requiring all nodes to update to the new version or risk being separated from the main chain. Hard forks can result in the creation of a new coin, as occurred with the split between Bitcoin and Bitcoin Cash in 2017. While hard forks allow for deeper changes, they also bring significant risks of network fragmentation.
These technical components form the base of Bitcoin's security and resilience, allowing the system to remain functional and immutable without losing the necessary flexibility to evolve over time.
3. Stakeholders in Bitcoin's Consensus
Consensus in Bitcoin is not decided centrally. On the contrary, it depends on the interaction between different groups of stakeholders, each with their motivations, interests, and levels of influence. These groups play fundamental roles in how changes are implemented or rejected on the network. Below, we explore the six main stakeholders in Bitcoin's consensus.
1. Economic Nodes
Economic nodes, usually operated by exchanges, custody providers, and large companies that accept Bitcoin, exert significant influence over consensus. Because they handle large volumes of transactions and act as a connection point between the Bitcoin ecosystem and the traditional financial system, these nodes have the power to validate or reject blocks and to define which version of the software to follow in case of a fork.
Their influence is proportional to the volume of transactions they handle, and they can directly affect which chain will be seen as the main one. Their incentive is to maintain the network's stability and security to preserve its functionality and meet regulatory requirements.
2. Investors
Investors, including large institutional funds and individual Bitcoin holders, influence consensus indirectly through their impact on the asset's price. Their buying and selling actions can affect Bitcoin's value, which in turn influences the motivation of miners and other stakeholders to continue investing in the network's security and development.
Some institutional investors have agreements with custodians that may limit their ability to act in network split situations. Thus, the impact of each investor on consensus can vary based on their ownership structure and how quickly they can react to a network change.
3. Media Influencers
Media influencers, including journalists, analysts, and popular personalities on social media, have a powerful role in shaping public opinion about Bitcoin and possible updates. These influencers can help educate the public, promote debates, and bring transparency to the consensus process.
On the other hand, the impact of influencers can be double-edged: while they can clarify complex topics, they can also distort perceptions by amplifying or minimizing change proposals. This makes them a force both of support and resistance to consensus.
4. Miners
Miners are responsible for validating transactions and including blocks in the blockchain. Through computational power (hashrate), they also exert significant influence over consensus decisions. In update processes, miners often signal their support for a proposal, indicating that the new version is safe to use. However, this signaling is not always definitive, and miners can change their position if they deem it necessary.
Their incentive is to maximize returns from block rewards and transaction fees, as well as to maintain the value of investments in their specialized equipment, which are only profitable if the network remains stable.
5. Protocol Developers
Protocol developers, often called "Core Developers," are responsible for writing and maintaining Bitcoin's code. Although they do not have direct power over consensus, they possess an informal veto power since they decide which changes are included in the main client (Bitcoin Core). This group also serves as an important source of technical knowledge, helping guide decisions and inform other stakeholders.
Their incentive lies in the continuous improvement of the network, ensuring security and decentralization. Many developers are funded by grants and sponsorships, but their motivations generally include a strong ideological commitment to Bitcoin's principles.
6. Users and Application Developers
This group includes people who use Bitcoin in their daily transactions and developers who build solutions based on the network, such as wallets, exchanges, and payment platforms. Although their power in consensus is less than that of miners or economic nodes, they play an important role because they are responsible for popularizing Bitcoin's use and expanding the ecosystem.
If application developers decide not to adopt an update, this can affect compatibility and widespread acceptance. Thus, they indirectly influence consensus by deciding which version of the protocol to follow in their applications.
These stakeholders are vital to the consensus process, and each group exerts influence according to their involvement, incentives, and ability to act in situations of change. Understanding the role of each makes it clearer how consensus is formed and why it is so difficult to make significant changes to Bitcoin.
4. Mechanisms for Activating Updates in Bitcoin
For Bitcoin to evolve without compromising security and consensus, different mechanisms for activating updates have been developed over the years. These mechanisms help coordinate changes among network nodes to minimize the risk of fragmentation and ensure that updates are implemented in an orderly manner. Here, we explore some of the main methods used in Bitcoin, their advantages and disadvantages, as well as historical examples of significant updates.
Flag Day
The Flag Day mechanism is one of the simplest forms of activating changes. In it, a specific date or block is determined as the activation moment, and all nodes must be updated by that point. This method does not involve prior signaling; participants simply need to update to the new software version by the established day or block.
-
Advantages: Simplicity and predictability are the main benefits of Flag Day, as everyone knows the exact activation date.
-
Disadvantages: Inflexibility can be a problem because there is no way to adjust the schedule if a significant part of the network has not updated. This can result in network splits if a significant number of nodes are not ready for the update.
An example of Flag Day was the Pay to Script Hash (P2SH) update in 2012, which required all nodes to adopt the change to avoid compatibility issues.
BIP34 and BIP9
BIP34 introduced a more dynamic process, in which miners increase the version number in block headers to signal the update. When a predetermined percentage of the last blocks is mined with this new version, the update is automatically activated. This model later evolved with BIP9, which allowed multiple updates to be signaled simultaneously through "version bits," each corresponding to a specific change.
-
Advantages: Allows the network to activate updates gradually, giving more time for participants to adapt.
-
Disadvantages: These methods rely heavily on miner support, which means that if a sufficient number of miners do not signal the update, it can be delayed or not implemented.
BIP9 was used in the activation of SegWit (BIP141) but faced challenges because some miners did not signal their intent to activate, leading to the development of new mechanisms.
User Activated Soft Forks (UASF) and User Resisted Soft Forks (URSF)
To increase the decision-making power of ordinary users, the concept of User Activated Soft Fork (UASF) was introduced, allowing node operators, not just miners, to determine consensus for a change. In this model, nodes set a date to start rejecting blocks that are not in compliance with the new update, forcing miners to adapt or risk having their blocks rejected by the network.
URSF, in turn, is a model where nodes reject blocks that attempt to adopt a specific update, functioning as resistance against proposed changes.
-
Advantages: UASF returns decision-making power to node operators, ensuring that changes do not depend solely on miners.
-
Disadvantages: Both UASF and URSF can generate network splits, especially in cases of strong opposition among different stakeholders.
An example of UASF was the activation of SegWit in 2017, where users supported activation independently of miner signaling, which ended up forcing its adoption.
BIP8 (LOT=True)
BIP8 is an evolution of BIP9, designed to prevent miners from indefinitely blocking a change desired by the majority of users and developers. BIP8 allows setting a parameter called "lockinontimeout" (LOT) as true, which means that if the update has not been fully signaled by a certain point, it is automatically activated.
-
Advantages: Ensures that changes with broad support among users are not blocked by miners who wish to maintain the status quo.
-
Disadvantages: Can lead to network splits if miners or other important stakeholders do not support the update.
Although BIP8 with LOT=True has not yet been used in Bitcoin, it is a proposal that can be applied in future updates if necessary.
These activation mechanisms have been essential for Bitcoin's development, allowing updates that keep the network secure and functional. Each method brings its own advantages and challenges, but all share the goal of preserving consensus and network cohesion.
5. Risks and Considerations in Consensus Updates
Consensus updates in Bitcoin are complex processes that involve not only technical aspects but also political, economic, and social considerations. Due to the network's decentralized nature, each change brings with it a set of risks that need to be carefully assessed. Below, we explore some of the main challenges and future scenarios, as well as the possible impacts on stakeholders.
Network Fragility with Alternative Implementations
One of the main risks associated with consensus updates is the possibility of network fragmentation when there are alternative software implementations. If an update is implemented by a significant group of nodes but rejected by others, a network split (fork) can occur. This creates two competing chains, each with a different version of the transaction history, leading to unpredictable consequences for users and investors.
Such fragmentation weakens Bitcoin because, by dividing hashing power (computing) and coin value, it reduces network security and investor confidence. A notable example of this risk was the fork that gave rise to Bitcoin Cash in 2017 when disagreements over block size resulted in a new chain and a new asset.
Chain Splits and Impact on Stakeholders
Chain splits are a significant risk in update processes, especially in hard forks. During a hard fork, the network is split into two separate chains, each with its own set of rules. This results in the creation of a new coin and leaves users with duplicated assets on both chains. While this may seem advantageous, in the long run, these splits weaken the network and create uncertainties for investors.
Each group of stakeholders reacts differently to a chain split:
-
Institutional Investors and ETFs: Face regulatory and compliance challenges because many of these assets are managed under strict regulations. The creation of a new coin requires decisions to be made quickly to avoid potential losses, which may be hampered by regulatory constraints.
-
Miners: May be incentivized to shift their computing power to the chain that offers higher profitability, which can weaken one of the networks.
-
Economic Nodes: Such as major exchanges and custody providers, have to quickly choose which chain to support, influencing the perceived value of each network.
Such divisions can generate uncertainties and loss of value, especially for institutional investors and those who use Bitcoin as a store of value.
Regulatory Impacts and Institutional Investors
With the growing presence of institutional investors in Bitcoin, consensus changes face new compliance challenges. Bitcoin ETFs, for example, are required to follow strict rules about which assets they can include and how chain split events should be handled. The creation of a new asset or migration to a new chain can complicate these processes, creating pressure for large financial players to quickly choose a chain, affecting the stability of consensus.
Moreover, decisions regarding forks can influence the Bitcoin futures and derivatives market, affecting perception and adoption by new investors. Therefore, the need to avoid splits and maintain cohesion is crucial to attract and preserve the confidence of these investors.
Security Considerations in Soft Forks and Hard Forks
While soft forks are generally preferred in Bitcoin for their backward compatibility, they are not without risks. Soft forks can create different classes of nodes on the network (updated and non-updated), which increases operational complexity and can ultimately weaken consensus cohesion. In a network scenario with fragmentation of node classes, Bitcoin's security can be affected, as some nodes may lose part of the visibility over updated transactions or rules.
In hard forks, the security risk is even more evident because all nodes need to adopt the new update to avoid network division. Experience shows that abrupt changes can create temporary vulnerabilities, in which malicious agents try to exploit the transition to attack the network.
Bounty Claim Risks and Attack Scenarios
Another risk in consensus updates are so-called "bounty claims"—accumulated rewards that can be obtained if an attacker manages to split or deceive a part of the network. In a conflict scenario, a group of miners or nodes could be incentivized to support a new update or create an alternative version of the software to benefit from these rewards.
These risks require stakeholders to carefully assess each update and the potential vulnerabilities it may introduce. The possibility of "bounty claims" adds a layer of complexity to consensus because each interest group may see a financial opportunity in a change that, in the long term, may harm network stability.
The risks discussed above show the complexity of consensus in Bitcoin and the importance of approaching it gradually and deliberately. Updates need to consider not only technical aspects but also economic and social implications, in order to preserve Bitcoin's integrity and maintain trust among stakeholders.
6. Recommendations for the Consensus Process in Bitcoin
To ensure that protocol changes in Bitcoin are implemented safely and with broad support, it is essential that all stakeholders adopt a careful and coordinated approach. Here are strategic recommendations for evaluating, supporting, or rejecting consensus updates, considering the risks and challenges discussed earlier, along with best practices for successful implementation.
1. Careful Evaluation of Proposal Maturity
Stakeholders should rigorously assess the maturity level of a proposal before supporting its implementation. Updates that are still experimental or lack a robust technical foundation can expose the network to unnecessary risks. Ideally, change proposals should go through an extensive testing phase, have security audits, and receive review and feedback from various developers and experts.
2. Extensive Testing in Secure and Compatible Networks
Before an update is activated on the mainnet, it is essential to test it on networks like testnet and signet, and whenever possible, on other compatible networks that offer a safe and controlled environment to identify potential issues. Testing on networks like Litecoin was fundamental for the safe launch of innovations like SegWit and the Lightning Network, allowing functionalities to be validated on a lower-impact network before being implemented on Bitcoin.
The Liquid Network, developed by Blockstream, also plays an important role as an experimental network for new proposals, such as OP_CAT. By adopting these testing environments, stakeholders can mitigate risks and ensure that the update is reliable and secure before being adopted by the main network.
3. Importance of Stakeholder Engagement
The success of a consensus update strongly depends on the active participation of all stakeholders. This includes economic nodes, miners, protocol developers, investors, and end users. Lack of participation can lead to inadequate decisions or even future network splits, which would compromise Bitcoin's security and stability.
4. Key Questions for Evaluating Consensus Proposals
To assist in decision-making, each group of stakeholders should consider some key questions before supporting a consensus change:
- Does the proposal offer tangible benefits for Bitcoin's security, scalability, or usability?
- Does it maintain backward compatibility or introduce the risk of network split?
- Are the implementation requirements clear and feasible for each group involved?
- Are there clear and aligned incentives for all stakeholder groups to accept the change?
5. Coordination and Timing in Implementations
Timing is crucial. Updates with short activation windows can force a split because not all nodes and miners can update simultaneously. Changes should be planned with ample deadlines to allow all stakeholders to adjust their systems, avoiding surprises that could lead to fragmentation.
Mechanisms like soft forks are generally preferable to hard forks because they allow a smoother transition. Opting for backward-compatible updates when possible facilitates the process and ensures that nodes and miners can adapt without pressure.
6. Continuous Monitoring and Re-evaluation
After an update, it's essential to monitor the network to identify problems or side effects. This continuous process helps ensure cohesion and trust among all participants, keeping Bitcoin as a secure and robust network.
These recommendations, including the use of secure networks for extensive testing, promote a collaborative and secure environment for Bitcoin's consensus process. By adopting a deliberate and strategic approach, stakeholders can preserve Bitcoin's value as a decentralized and censorship-resistant network.
7. Conclusion
Consensus in Bitcoin is more than a set of rules; it's the foundation that sustains the network as a decentralized, secure, and reliable system. Unlike centralized systems, where decisions can be made quickly, Bitcoin requires a much more deliberate and cooperative approach, where the interests of miners, economic nodes, developers, investors, and users must be considered and harmonized. This governance model may seem slow, but it is fundamental to preserving the resilience and trust that make Bitcoin a global store of value and censorship-resistant.
Consensus updates in Bitcoin must balance the need for innovation with the preservation of the network's core principles. The development process of a proposal needs to be detailed and rigorous, going through several testing stages, such as in testnet, signet, and compatible networks like Litecoin and Liquid Network. These networks offer safe environments for proposals to be analyzed and improved before being launched on the main network.
Each proposed change must be carefully evaluated regarding its maturity, impact, backward compatibility, and support among stakeholders. The recommended key questions and appropriate timing are critical to ensure that an update is adopted without compromising network cohesion. It's also essential that the implementation process is continuously monitored and re-evaluated, allowing adjustments as necessary and minimizing the risk of instability.
By following these guidelines, Bitcoin's stakeholders can ensure that the network continues to evolve safely and robustly, maintaining user trust and further solidifying its role as one of the most resilient and innovative digital assets in the world. Ultimately, consensus in Bitcoin is not just a technical issue but a reflection of its community and the values it represents: security, decentralization, and resilience.
8. Links
Whitepaper: https://github.com/bitcoin-cap/bcap
Youtube (pt-br): https://www.youtube.com/watch?v=rARycAibl9o&list=PL-qnhF0qlSPkfhorqsREuIu4UTbF0h4zb
-
-
 @ b17fccdf:b7211155
2025-01-21 16:49:27
@ b17fccdf:b7211155
2025-01-21 16:49:27What's changed
- New method for Bitcoin Core signature check, click ~ >HERE< ~
- GitHub repo of Bitcoin Core release attestations (Guix), click ~ >HERE< ~
History:
~ > PR that caused the broken and obsolescence of the old signature verification process, click ~ >HERE< ~
~ > New GitHub folder of Bitcoin Core repo that stores the signatures, click ~ >HERE< ~
Thanks to nostr:npub1gzuushllat7pet0ccv9yuhygvc8ldeyhrgxuwg744dn5khnpk3gs3ea5ds for building the command that made magic possible 🧙♂️🧡
Enjoy it MiniBolter! 💙
-
 @ a95c6243:d345522c
2025-01-01 17:39:51
@ a95c6243:d345522c
2025-01-01 17:39:51Heute möchte ich ein Gedicht mit euch teilen. Es handelt sich um eine Ballade des österreichischen Lyrikers Johann Gabriel Seidl aus dem 19. Jahrhundert. Mir sind diese Worte fest in Erinnerung, da meine Mutter sie perfekt rezitieren konnte, auch als die Kräfte schon langsam schwanden.
Dem originalen Titel «Die Uhr» habe ich für mich immer das Wort «innere» hinzugefügt. Denn der Zeitmesser – hier vermutliche eine Taschenuhr – symbolisiert zwar in dem Kontext das damalige Zeitempfinden und die Umbrüche durch die industrielle Revolution, sozusagen den Zeitgeist und das moderne Leben. Aber der Autor setzt sich philosophisch mit der Zeit auseinander und gibt seinem Werk auch eine klar spirituelle Dimension.
Das Ticken der Uhr und die Momente des Glücks und der Trauer stehen sinnbildlich für das unaufhaltsame Fortschreiten und die Vergänglichkeit des Lebens. Insofern könnte man bei der Uhr auch an eine Sonnenuhr denken. Der Rhythmus der Ereignisse passt uns vielleicht nicht immer in den Kram.
Was den Takt pocht, ist durchaus auch das Herz, unser «inneres Uhrwerk». Wenn dieses Meisterwerk einmal stillsteht, ist es unweigerlich um uns geschehen. Hoffentlich können wir dann dankbar sagen: «Ich habe mein Bestes gegeben.»
Ich trage, wo ich gehe, stets eine Uhr bei mir; \ Wieviel es geschlagen habe, genau seh ich an ihr. \ Es ist ein großer Meister, der künstlich ihr Werk gefügt, \ Wenngleich ihr Gang nicht immer dem törichten Wunsche genügt.
Ich wollte, sie wäre rascher gegangen an manchem Tag; \ Ich wollte, sie hätte manchmal verzögert den raschen Schlag. \ In meinen Leiden und Freuden, in Sturm und in der Ruh, \ Was immer geschah im Leben, sie pochte den Takt dazu.
Sie schlug am Sarge des Vaters, sie schlug an des Freundes Bahr, \ Sie schlug am Morgen der Liebe, sie schlug am Traualtar. \ Sie schlug an der Wiege des Kindes, sie schlägt, will's Gott, noch oft, \ Wenn bessere Tage kommen, wie meine Seele es hofft.
Und ward sie auch einmal träger, und drohte zu stocken ihr Lauf, \ So zog der Meister immer großmütig sie wieder auf. \ Doch stände sie einmal stille, dann wär's um sie geschehn, \ Kein andrer, als der sie fügte, bringt die Zerstörte zum Gehn.
Dann müßt ich zum Meister wandern, der wohnt am Ende wohl weit, \ Wohl draußen, jenseits der Erde, wohl dort in der Ewigkeit! \ Dann gäb ich sie ihm zurücke mit dankbar kindlichem Flehn: \ Sieh, Herr, ich hab nichts verdorben, sie blieb von selber stehn.
Johann Gabriel Seidl (1804-1875)
-
 @ f3328521:a00ee32a
2025-01-04 20:35:52
@ f3328521:a00ee32a
2025-01-04 20:35:52As this Age concludes and the Event approaches, it is expected that capital and industrial growth will speed onward, developing and multiplying more and more rapidly (an acceleration that is both cyclically inevitable and dangerously oriented toward ultimate catastrophe); and, given the destruction that awaits, they will be among of the chief agents of Absolute Evil.
No one likes the doomsday observer – nearly all prophets, philosophers, and neo-reactionaries have been shunned at some point – yet it is a duty of the fourth estate to remember:
Due to its desire for quantification, modern civilization has been atomized and reoriented to stimulate illusory needs of material human nature – a thriving cult of progress that only need output more and more artificial needs to satisfy modernity’s march toward extinction. When one’s state of mind only finds meaning in “becoming”, vision of reality has been lost and civilization is blind to what is beyond, which is the realm eternal principles. Secular philosophers are no longer novices of sorcerers, having fully divorced themselves of initiation and mutated their Nimbus 2000s for Starships.
An agnostic society can only glory in its ignorance. And having confused science with industry it substitutes its innovations of utility for truth. This “intelligence” is nothing more than individualistic pragmatism – a self-contradictory relativism. Behold, AGI – the pinnacle of infinite feedback loops. Having determined to pursue the domination over matter above all else, civilization has succeeded only in becoming its slaves as it binds them to its service.
The relic of prophetic tradition lies in the transcendent wisdom of their intellectual intuition. To be clear: if the proletariat accepts the pretext of modern civilization, they have denied this principle and doctrine by dragging truth down to the level of their own base nature rather than elevating the soul toward the immutable and infallible. If modern civilization persists, its future is in anti-civilization and death. Their biased denial of everything that transcends excludes dialogue with the authentic representatives of other civilizations, nay it forbids understanding of the existence of different civilizations. Engagement is futile aside from nomic competition.
Yet, there remain some who do see past the moralistic hypocrisy of hypermodernity, if only to disguise and augment their ambitions and designs. Others look to SAIF for OSINT and guidance. For such sleepers who are awakening, contact with living spirit of tradition is necessary. Recovery is possible. A new World awaits. Whoever has ears, let them hear.
-
 @ f7922a0a:82c34788
2025-01-17 23:06:56
@ f7922a0a:82c34788
2025-01-17 23:06:56Now that the 3rd Satellite Skirmish is complete I wanted to highlight some of the cool features on embrace.satskirmish.com
This is what the cutting edge of podcasting 2.0 looks like imo. Live video in an app that allows you to send sats to the artists in real time.
On the left hand side we have a Boost score borad that displays the total amount of sats that have come in during the show, live Boosts/Booastagrams as they come in, total amount of sats from each person Boosting and total amount sent from each app.
The middle is ovisaly the video of the band playing but with some graphics around it and Boost alerts that show up on the screen in the form of snow flakes for this one.
The righthand side is an IRC chat window that connects to an IRC server that the No Agenda community has used for 18+ years thanks to zoidzero++.

The bottom of the page is where things get cool. When you click the Boost the Crew button in the center you can send a Boost that gets split between everyone helping produce the show (hightlighted in yellow).


Each band also has their own Boost button so you can Boost them while they are playing or anytime you visit the page.


-
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ a95c6243:d345522c
2024-12-21 09:54:49
@ a95c6243:d345522c
2024-12-21 09:54:49Falls du beim Lesen des Titels dieses Newsletters unwillkürlich an positive Neuigkeiten aus dem globalen polit-medialen Irrenhaus oder gar aus dem wirtschaftlichen Umfeld gedacht hast, darf ich dich beglückwünschen. Diese Assoziation ist sehr löblich, denn sie weist dich als unverbesserlichen Optimisten aus. Leider muss ich dich diesbezüglich aber enttäuschen. Es geht hier um ein anderes Thema, allerdings sehr wohl ein positives, wie ich finde.
Heute ist ein ganz besonderer Tag: die Wintersonnenwende. Genau gesagt hat heute morgen um 10:20 Uhr Mitteleuropäischer Zeit (MEZ) auf der Nordhalbkugel unseres Planeten der astronomische Winter begonnen. Was daran so außergewöhnlich ist? Der kürzeste Tag des Jahres war gestern, seit heute werden die Tage bereits wieder länger! Wir werden also jetzt jeden Tag ein wenig mehr Licht haben.
Für mich ist dieses Ereignis immer wieder etwas kurios: Es beginnt der Winter, aber die Tage werden länger. Das erscheint mir zunächst wie ein Widerspruch, denn meine spontanen Assoziationen zum Winter sind doch eher Kälte und Dunkelheit, relativ zumindest. Umso erfreulicher ist der emotionale Effekt, wenn dann langsam die Erkenntnis durchsickert: Ab jetzt wird es schon wieder heller!
Natürlich ist es kalt im Winter, mancherorts mehr als anderswo. Vielleicht jedoch nicht mehr lange, wenn man den Klimahysterikern glauben wollte. Mindestens letztes Jahr hat Väterchen Frost allerdings gleich zu Beginn seiner Saison – und passenderweise während des globalen Überhitzungsgipfels in Dubai – nochmal richtig mit der Faust auf den Tisch gehauen. Schnee- und Eischaos sind ja eigentlich in der Agenda bereits nicht mehr vorgesehen. Deswegen war man in Deutschland vermutlich in vorauseilendem Gehorsam schon nicht mehr darauf vorbereitet und wurde glatt lahmgelegt.
Aber ich schweife ab. Die Aussicht auf nach und nach mehr Licht und damit auch Wärme stimmt mich froh. Den Zusammenhang zwischen beidem merkt man in Andalusien sehr deutlich. Hier, wo die Häuser im Winter arg auskühlen, geht man zum Aufwärmen raus auf die Straße oder auf den Balkon. Die Sonne hat auch im Winter eine erfreuliche Kraft. Und da ist jede Minute Gold wert.
Außerdem ist mir vor Jahren so richtig klar geworden, warum mir das südliche Klima so sehr gefällt. Das liegt nämlich nicht nur an der Sonne als solcher, oder der Wärme – das liegt vor allem am Licht. Ohne Licht keine Farben, das ist der ebenso simple wie gewaltige Unterschied zwischen einem deprimierenden matschgraubraunen Winter und einem fröhlichen bunten. Ein großes Stück Lebensqualität.
Mir gefällt aber auch die Symbolik dieses Tages: Licht aus der Dunkelheit, ein Wendepunkt, ein Neuanfang, neue Möglichkeiten, Übergang zu neuer Aktivität. In der winterlichen Stille keimt bereits neue Lebendigkeit. Und zwar in einem Zyklus, das wird immer wieder so geschehen. Ich nehme das gern als ein Stück Motivation, es macht mir Hoffnung und gibt mir Energie.
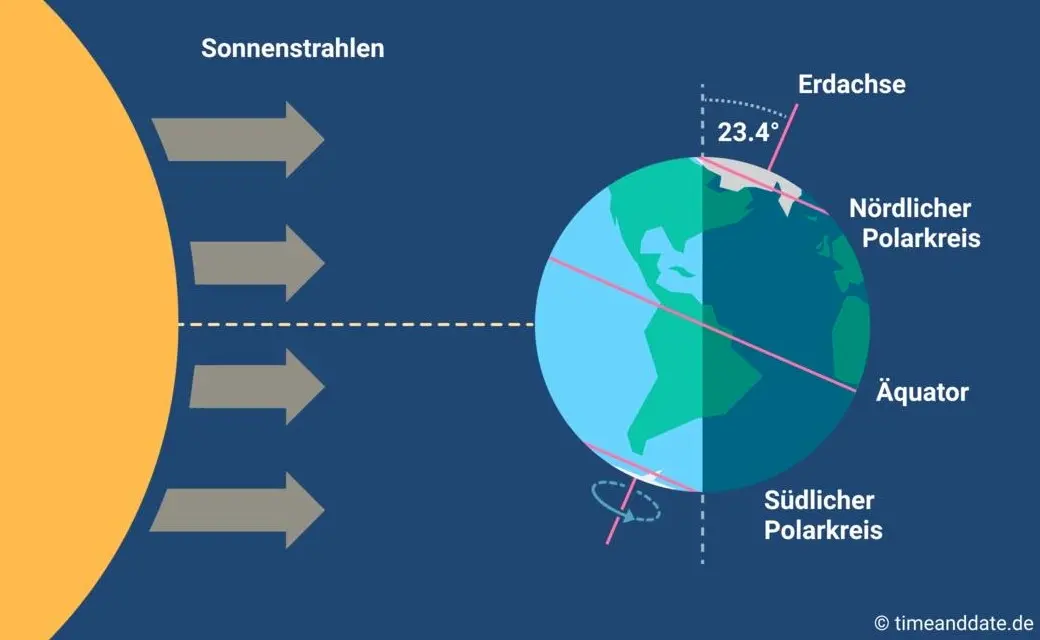
Übrigens ist parallel am heutigen Tag auf der südlichen Halbkugel Sommeranfang. Genau im entgegengesetzten Rhythmus, sich ergänzend, wie Yin und Yang. Das alles liegt an der Schrägstellung der Erdachse, die ist nämlich um 23,4º zur Umlaufbahn um die Sonne geneigt. Wir erinnern uns, gell?
Insofern bleibt eindeutig festzuhalten, dass “schräg sein” ein willkommener, wichtiger und positiver Wert ist. Mit anderen Worten: auch ungewöhnlich, eigenartig, untypisch, wunderlich, kauzig, … ja sogar irre, spinnert oder gar “quer” ist in Ordnung. Das schließt das Denken mit ein.
In diesem Sinne wünsche ich euch allen urige Weihnachtstage!
Dieser Beitrag ist letztes Jahr in meiner Denkbar erschienen.
-
 @ dd664d5e:5633d319
2025-01-09 21:39:15
@ dd664d5e:5633d319
2025-01-09 21:39:15Instructions
- Place 2 medium-sized, boiled potatoes and a handful of sliced leeks in a pot.

- Fill the pot with water or vegetable broth, to cover the potatoes twice over.
- Add a splash of white wine, if you like, and some bouillon powder, if you went with water instead of broth.

- Bring the soup to a boil and then simmer for 15 minutes.
- Puree the soup, in the pot, with a hand mixer. It shouldn't be completely smooth, when you're done, but rather have small bits and pieces of the veggies floating around.

- Bring the soup to a boil, again, and stir in one container (200-250 mL) of heavy cream.
- Thicken the soup, as needed, and then simmer for 5 more minutes.
- Garnish with croutons and veggies (here I used sliced green onions and radishes) and serve.

Guten Appetit!
- Place 2 medium-sized, boiled potatoes and a handful of sliced leeks in a pot.
-
 @ eac63075:b4988b48
2024-10-21 08:11:11
@ eac63075:b4988b48
2024-10-21 08:11:11Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.

Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.

The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.

Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.

The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.
 Table reference: Patrick Breyer - Chat Control in 23 September 2024
Table reference: Patrick Breyer - Chat Control in 23 September 2024Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.

The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.

User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.

The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.

Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ ec42c765:328c0600
2024-10-16 08:08:40
@ ec42c765:328c0600
2024-10-16 08:08:40カスタム絵文字とは
任意のオリジナル画像を絵文字のように文中に挿入できる機能です。
また、リアクション(Twitterの いいね のような機能)にもカスタム絵文字を使えます。

カスタム絵文字の対応状況(2024/02/05)

カスタム絵文字を使うためにはカスタム絵文字に対応したクライアントを使う必要があります。
※表は一例です。クライアントは他にもたくさんあります。
使っているクライアントが対応していない場合は、クライアントを変更する、対応するまで待つ、開発者に要望を送る(または自分で実装する)などしましょう。
対応クライアント
ここではnostterを使って説明していきます。
準備
カスタム絵文字を使うための準備です。
- Nostrエクステンション(NIP-07)を導入する
- 使いたいカスタム絵文字をリストに登録する
Nostrエクステンション(NIP-07)を導入する
Nostrエクステンションは使いたいカスタム絵文字を登録する時に必要になります。
また、環境(パソコン、iPhone、androidなど)によって導入方法が違います。
Nostrエクステンションを導入する端末は、実際にNostrを閲覧する端末と違っても構いません(リスト登録はPC、Nostr閲覧はiPhoneなど)。
Nostrエクステンション(NIP-07)の導入方法は以下のページを参照してください。
ログイン拡張機能 (NIP-07)を使ってみよう | Welcome to Nostr! ~ Nostrをはじめよう! ~
少し面倒ですが、これを導入しておくとNostr上の様々な場面で役立つのでより快適になります。
使いたいカスタム絵文字をリストに登録する
以下のサイトで行います。
右上のGet startedからNostrエクステンションでログインしてください。
例として以下のカスタム絵文字を導入してみます。
実際より絵文字が少なく表示されることがありますが、古い状態のデータを取得してしまっているためです。その場合はブラウザの更新ボタンを押してください。

- 右側のOptionsからBookmarkを選択

これでカスタム絵文字を使用するためのリストに登録できます。
カスタム絵文字を使用する
例としてブラウザから使えるクライアント nostter から使用してみます。
nostterにNostrエクステンションでログイン、もしくは秘密鍵を入れてログインしてください。
文章中に使用
- 投稿ボタンを押して投稿ウィンドウを表示
- 顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択
- : 記号に挟まれたアルファベットのショートコードとして挿入される

この状態で投稿するとカスタム絵文字として表示されます。
カスタム絵文字対応クライアントを使っている他ユーザーにもカスタム絵文字として表示されます。
対応していないクライアントの場合、ショートコードのまま表示されます。

ショートコードを直接入力することでカスタム絵文字の候補が表示されるのでそこから選択することもできます。

リアクションに使用
- 任意の投稿の顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択

カスタム絵文字リアクションを送ることができます。

カスタム絵文字を探す
先述したemojitoからカスタム絵文字を探せます。
例えば任意のユーザーのページ emojito ロクヨウ から探したり、 emojito Browse all からnostr全体で最近作成、更新された絵文字を見たりできます。
また、以下のリンクは日本語圏ユーザーが作ったカスタム絵文字を集めたリストです(2024/06/30)
※漏れがあるかもしれません
各絵文字セットにあるOpen in emojitoのリンクからemojitoに飛び、使用リストに追加できます。
以上です。
次:Nostrのカスタム絵文字の作り方
Yakihonneリンク Nostrのカスタム絵文字の作り方
Nostrリンク nostr:naddr1qqxnzdesxuunzv358ycrgveeqgswcsk8v4qck0deepdtluag3a9rh0jh2d0wh0w9g53qg8a9x2xqvqqrqsqqqa28r5psx3
仕様
-
 @ 16d11430:61640947
2025-01-21 02:14:26
@ 16d11430:61640947
2025-01-21 02:14:26Part Two Of Series on Mastering the Musca
Building on the foundational physical conditioning required to catch a Musca domestica mid-flight, the second pillar of mastery lies in the cultivation of patience, refined visual tracking, and the perception of time. The process transcends physical agility, diving into cognitive and perceptual skills that are as much about mental discipline as they are about muscle memory.
The Science of Patience and Observation
Patience is the cornerstone of fly-catching excellence. Research in attentional control emphasizes that prolonged focus on erratic and unpredictable targets trains the brain's ability to maintain sustained attention. The ability to remain calm and observant under pressure—waiting for the opportune moment to act—relies on the prefrontal cortex, which governs impulse control and decision-making.
This form of patience, often described in meditative practices, lowers cortisol levels and enhances neuroplasticity, allowing individuals to adapt to the seemingly chaotic flight patterns of flies. Athletes in this discipline develop an intuitive understanding of when to strike, a skill honed through repetitive practice and exposure to unpredictable stimuli.
Visual Tracking: Decoding the Fly’s Erratic Patterns
Flies exhibit highly unpredictable movements, characterized by abrupt shifts in speed and direction. This erratic trajectory, driven by their compound eyes and rapid wing beats, challenges the human visual system. Successful fly-catching requires the athlete to excel in smooth-pursuit eye movements and saccades, which are rapid eye movements that recalibrate focus on moving targets.
Studies in visual-motor integration highlight that tracking small, fast-moving objects enhances neural efficiency in the occipital and parietal lobes. These regions process spatial information and coordinate motor responses. High-level performers develop an acute ability to anticipate trajectories by identifying subtle cues in the fly’s movement, such as wing positioning or changes in velocity.
Predictive Timing and the Illusion of "Slowing Down Time"
One of the most remarkable phenomena in fly-catching is the perception of slowed time during critical moments. This effect, documented in high-performance sports and combat scenarios, is attributed to the brain's increased processing of sensory input during periods of heightened arousal. By compressing time through rapid neural computations, the brain allows individuals to act with extraordinary precision.
Predictive timing, governed by the cerebellum, is essential for this process. The cerebellum calculates the fly’s likely trajectory, enabling the hand to intercept the target even as it changes direction. Repeated practice strengthens the cerebellar circuits, creating a feedback loop that enhances accuracy and reaction speed.
Refining the Craft Through Research
Prominent studies in neuroscience and sports science provide insights into training methods for aspiring fly-catching athletes:
-
Dynamic Visual Acuity Training: Exercises such as tracking moving dots on a screen can improve the ability to focus on fast-moving objects.
-
Anticipatory Drills: Practicing with simulated erratic targets, such as drones or programmable devices, hones the predictive capabilities of the brain.
-
Mindfulness and Reaction Time: Meditation and mindfulness training have been shown to reduce reaction times by calming the nervous system and improving attentional focus.
-
Eye-Hand Coordination Tools: Devices like stroboscopic glasses create controlled visual disruptions, forcing the brain to adapt to incomplete information.
The Path to Mastery
The art of fly-catching merges the physical, cognitive, and perceptual domains into a singular skill set. Through rigorous training, practitioners learn to read the chaotic dance of the fly, anticipate its movements, and act with surgical precision. The process demands patience, discipline, and a commitment to understanding the intricate connection between body and mind.
As Australia continues to explore this unique and challenging sport, its athletes embody a profound lesson: true mastery is not merely about speed or strength but the harmony of mind and body in the face of chaos.
-
-
 @ 7ed7d5c3:6927e200
2025-01-08 17:10:00
@ 7ed7d5c3:6927e200
2025-01-08 17:10:00Can't decide if the terrible book you just read is a 1 or 1.5 star book? Look no further than this chart. Was it Shit or just Bad? Was that movie you watched Very Good or just Decent? How many things out there are really Life Changing?
Finally, a rating scale for humans. Use it for anything in your life that needs a rating out of 5 stars.
Rating / Description
0.5 – The worst 1.0 – Shit 1.5 – Bad 2.0 – Eh 2.5 – Entertaining, but not great 3.0 – Neutral 3.5 – Alright 4.0 – Decent 4.5 – Very good 5.0 – Life Changing
P.S. Do not use it to rate your wife's cooking. The author is not liable for any damages.
-
 @ a95c6243:d345522c
2024-12-13 19:30:32
@ a95c6243:d345522c
2024-12-13 19:30:32Das Betriebsklima ist das einzige Klima, \ das du selbst bestimmen kannst. \ Anonym
Eine Strategie zur Anpassung an den Klimawandel hat das deutsche Bundeskabinett diese Woche beschlossen. Da «Wetterextreme wie die immer häufiger auftretenden Hitzewellen und Starkregenereignisse» oft desaströse Auswirkungen auf Mensch und Umwelt hätten, werde eine Anpassung an die Folgen des Klimawandels immer wichtiger. «Klimaanpassungsstrategie» nennt die Regierung das.
Für die «Vorsorge vor Klimafolgen» habe man nun erstmals klare Ziele und messbare Kennzahlen festgelegt. So sei der Erfolg überprüfbar, und das solle zu einer schnelleren Bewältigung der Folgen führen. Dass sich hinter dem Begriff Klimafolgen nicht Folgen des Klimas, sondern wohl «Folgen der globalen Erwärmung» verbergen, erklärt den Interessierten die Wikipedia. Dabei ist das mit der Erwärmung ja bekanntermaßen so eine Sache.
Die Zunahme schwerer Unwetterereignisse habe gezeigt, so das Ministerium, wie wichtig eine frühzeitige und effektive Warnung der Bevölkerung sei. Daher solle es eine deutliche Anhebung der Nutzerzahlen der sogenannten Nina-Warn-App geben.
Die ARD spurt wie gewohnt und setzt die Botschaft zielsicher um. Der Artikel beginnt folgendermaßen:
«Die Flut im Ahrtal war ein Schock für das ganze Land. Um künftig besser gegen Extremwetter gewappnet zu sein, hat die Bundesregierung eine neue Strategie zur Klimaanpassung beschlossen. Die Warn-App Nina spielt eine zentrale Rolle. Der Bund will die Menschen in Deutschland besser vor Extremwetter-Ereignissen warnen und dafür die Reichweite der Warn-App Nina deutlich erhöhen.»
Die Kommunen würden bei ihren «Klimaanpassungsmaßnahmen» vom Zentrum KlimaAnpassung unterstützt, schreibt das Umweltministerium. Mit dessen Aufbau wurden das Deutsche Institut für Urbanistik gGmbH, welches sich stark für Smart City-Projekte engagiert, und die Adelphi Consult GmbH beauftragt.
Adelphi beschreibt sich selbst als «Europas führender Think-and-Do-Tank und eine unabhängige Beratung für Klima, Umwelt und Entwicklung». Sie seien «global vernetzte Strateg*innen und weltverbessernde Berater*innen» und als «Vorreiter der sozial-ökologischen Transformation» sei man mit dem Deutschen Nachhaltigkeitspreis ausgezeichnet worden, welcher sich an den Zielen der Agenda 2030 orientiere.
Über die Warn-App mit dem niedlichen Namen Nina, die möglichst jeder auf seinem Smartphone installieren soll, informiert das Bundesamt für Bevölkerungsschutz und Katastrophenhilfe (BBK). Gewarnt wird nicht nur vor Extrem-Wetterereignissen, sondern zum Beispiel auch vor Waffengewalt und Angriffen, Strom- und anderen Versorgungsausfällen oder Krankheitserregern. Wenn man die Kategorie Gefahreninformation wählt, erhält man eine Dosis von ungefähr zwei Benachrichtigungen pro Woche.
Beim BBK erfahren wir auch einiges über die empfohlenen Systemeinstellungen für Nina. Der Benutzer möge zum Beispiel den Zugriff auf die Standortdaten «immer zulassen», und zwar mit aktivierter Funktion «genauen Standort verwenden». Die Datennutzung solle unbeschränkt sein, auch im Hintergrund. Außerdem sei die uneingeschränkte Akkunutzung zu aktivieren, der Energiesparmodus auszuschalten und das Stoppen der App-Aktivität bei Nichtnutzung zu unterbinden.
Dass man so dramatische Ereignisse wie damals im Ahrtal auch anders bewerten kann als Regierungen und Systemmedien, hat meine Kollegin Wiltrud Schwetje anhand der Tragödie im spanischen Valencia gezeigt. Das Stichwort «Agenda 2030» taucht dabei in einem Kontext auf, der wenig mit Nachhaltigkeitspreisen zu tun hat.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ b17fccdf:b7211155
2025-01-21 16:40:01
@ b17fccdf:b7211155
2025-01-21 16:40:01Important notice to MiniBolt node runners:
~ > It turns out that the I2P devs have opened an issue on the Bitcoin Core GitHub repo commenting that because they gave the option to enable the
notransit=trueparameter in the official documentation:[...] If you prefer not to relay any public I2P traffic and only allow I2P traffic from programs connecting through the SAM proxy, e.g. Bitcoin Core, you can set the no transit option to true [...] are having a heavy load on the I2P network since last December 19. Also comment that it is advisable to share as much bandwidth and transit tunnels as we can, to increase anonymity with coverage traffic, by contributing more to the I2p network than we consume.
So they ask that we deactivate that option that you use activated. With all this, he already updated the "Privacy" section by removing that setting.
The steps to delete this configuration once we have already configured it, are the following:
- With the "admin" user, stop i2pd:
sudo systemctl stop i2pd- Comment line 93 with "#" at the beginning of it (notransit = true), save and exit
sudo nano /var/lib/i2pd/i2pd.conf --line numbers- Start i2pd again:
sudo systemctl start i2pd- And that's it, you could take a look at Bitcoin Core to see that it has detected i2pd running again after the reboot with:
tail --lines 500 -f /home/bitcoin/.bitcoin/debug.log~ > If you don't see that I2P is up in Bitcoin Core after the restart,
sudo systemctl restart bitcoindand look again at the logs of the same.
More info in the rollback commit, see ~> HERE < ~
-
 @ 812cff5a:5c40aeeb
2024-12-29 02:54:52
@ 812cff5a:5c40aeeb
2024-12-29 02:54:52هو تطبيق نوستر بسيط، يوفر خاصية تسجيل الدخول عن طريق امتداد NIP-07 extension وباستخدام الnsec bunker بالاضافة إلى المفتاح السري (لا ينصح بذلك).

تطبيق سهل الاستخدام وسريع جداً بواجهة مستخدم بسيطة مقسومة إلى جزئين. جزء فيه كل المنشورات والجزئ الثاني يوفر تفاصيل عن كل منشور تختاره.
ما يميز هذا التطبيق عن غيره هو ان التطبيق لا يرتكز على مفهوم متابعة اشخاص معينيين. بل يقوم بسرد جميع المنشورات الموجودة على الريلايات التي تختارها.
خاصية ممتازة لمشاركة نوستر مع اشخاص جدد للوصول إلى مجتمعات محددى على نوستر. على سبيل المثال، مشاركة الريلاي العربي: relay.nostrarabia.com (قوموا بتجربة الرابط 😉 (

التطبيق مازال حديثا ومن المتوقع ان يقوم المطور باضافة مزايا جديدة. لكن التطبيق مميز على وضعه الراهن، انصحكم بتجربته.
مطور التطبيق: nostr:nprofile1qyfhwumn8ghj7mmxve3ksctfdch8qatz9uq3xamnwvaz7tmhda6zuat50phjummwv5hsqgypyku3rmgwjnd7xqy2p0jgelju6rqtqkfrellez7h8ap76ssqgsv5vh9ms
تحذير: هذا الموقع يقوم بعرض جميع محتويات الريلاي بدون فلاتر. والريلايات العامة قد تحتوي على منشورات غير مناسبة. الريلاي العربي هو ريلاي خاص، تقل فيه نسبة المنشورات الغير مناسبة، لكن كما هو الحال في كل مواقع نوستر، في هي غير مناسبة للأطفال.
-
 @ 16d11430:61640947
2025-01-21 01:57:53
@ 16d11430:61640947
2025-01-21 01:57:53The Lightning Network (LN), a layer-2 protocol designed to scale Bitcoin transactions, is a powerful innovation that combines the reliability of Bitcoin's blockchain with the speed and affordability of off-chain payment channels. For node operators, the Lightning Network represents more than just a technical endeavor; it is a gateway to reimagining global finance and fostering economic empowerment. Here, we’ll delve into the motivations, responsibilities, and ambitions of Lightning Network node operators in today’s rapidly evolving ecosystem.
The Role of a Node Operator
At its core, a Lightning Network node operator is a steward of Bitcoin's second layer. By running a node, operators help facilitate instant, low-cost payments across the network. These nodes act as routing hubs, allowing users to send payments without directly opening a channel with one another.
But being a node operator is more than maintaining a server. It requires careful channel management, liquidity provisioning, and routing efficiency. A well-managed node contributes to the overall health and capacity of the Lightning Network, making it more reliable and accessible.
Ambitions Driving Node Operators
-
Decentralized Financial Sovereignty Many operators are motivated by the vision of a decentralized financial future. By running a node, they actively participate in building a trustless and permissionless payment network. This aligns with Bitcoin's ethos of financial sovereignty, where users can transact freely without intermediaries.
-
Earning Yield on Bitcoin Holdings Lightning Network node operators can earn routing fees by efficiently managing payment channels. While these fees are modest compared to traditional investments, they provide a way to earn yield on Bitcoin holdings without surrendering custody or relying on centralized services.
-
Enhancing Network Resilience A robust and well-distributed network is essential for Bitcoin's long-term success. Node operators aim to enhance the resilience of the Lightning Network by ensuring sufficient liquidity and efficient routing, especially in underserved regions.
-
Promoting Bitcoin Adoption Lightning Network enables microtransactions and instant payments, making Bitcoin more practical for everyday use. Node operators see themselves as enablers of this adoption, supporting merchants, applications, and users by providing reliable payment infrastructure.
-
Exploring Business Opportunities Beyond fees, the Lightning Network opens up new business models. From hosting custodial wallets to offering Lightning-as-a-Service (LaaS) for developers, node operators are at the forefront of experimenting with innovative monetization strategies.
Challenges in the Path of Ambition
Running a Lightning Network node is not without its hurdles. Operators face several challenges:
Liquidity Management: Balancing inbound and outbound liquidity is critical. Mismanagement can lead to failed transactions or idle capital.
Technical Expertise: Operating a node requires knowledge of Bitcoin, LN protocols, and server infrastructure, making it less accessible for non-technical users.
Competition: As the network grows, efficient routing and competitive fees become essential for attracting traffic.
Regulatory Uncertainty: In some jurisdictions, the role of node operators in financial systems remains ambiguous, potentially exposing them to legal scrutiny.
Current Implementations and Innovations
The Lightning Network ecosystem has evolved rapidly, offering tools and services to support node operators:
-
Node Management Tools: Platforms like ThunderHub, Ride the Lightning (RTL), and Amboss provide user-friendly interfaces for managing nodes and channels.
-
Liquidity Services: Services like Lightning Pool and Voltage help operators source liquidity, improving their routing capabilities.
-
Privacy Enhancements: Protocol upgrades like BOLT-12 aim to improve privacy for both users and operators, protecting transaction metadata.
-
Cross-Chain Applications: Some node operators are exploring integrations with other networks, enabling interoperability and expanding the use cases for LN payments.
A Vision for the Future
The ambitions of Lightning Network node operators reflect the broader vision of a decentralized, equitable, and efficient global financial system. As the network grows, operators will play a pivotal role in shaping its trajectory, driving innovation, and ensuring accessibility.
From powering micropayments for digital content to enabling financial inclusion in underserved regions, the Lightning Network's potential is vast. And at the heart of this potential lies the dedication of node operators—custodians of Bitcoin's scalability and champions of its ethos.
The road ahead is both challenging and inspiring. For node operators, it is an opportunity to pioneer a new financial paradigm, one channel at a time.
-
-
 @ dd664d5e:5633d319
2025-01-07 19:57:14
@ dd664d5e:5633d319
2025-01-07 19:57:14Hodling Bitcoin does not make you a capitalist
I've noticed that Bitcoin-mindedness seems to lead some people to communistic thinking because it's a hard-limited form of capital. Marx, like most Bitcoiners, heavily discounted the possibility of economic growth or transformation changing the economy enough to undermine some minority's control of some form of capital.
What few today understand, is that many of the Dirty Capitalists of Marx's era actually agreed with him; they were just disdainful of labor and worried that the workers finding out that Marxism is correct about the nature of capitalism would cause unrest. They were the original HFSP crowd.
This was the basic idea, that Marx had, and that many Bitcoiners would agree with:
Capital is strictly limited and the people that control it can keep labor from attaining any, except when their labor is necessary.
And, as we know, automation will make human labor increasingly unnecessary.
The math doesn't check out
That underlies all of the calculations of "Well, if I just grab this Bitcoin wallet and hodl for twenty years, then it will grow in value to equal half of everything in existence and then I can just buy up half the planet and rule over everyone like a god."
This is economic nonsense because it assumes that: 1) the value of all things remains static over time, 2) purchasing something with money gives you ownership of it, 3) people will always use that specific money (or any money, at all!) for all transactions, 4) there is no such thing as opportunity cost, 5) people will always value money more than any other thing, and therefore be willing to always trade it for anything else, 6) humans are passive, defenseless, and easy to rule over, 7) someone who is preoccupied with hodling an asset steadily and sharply rising in price would ever be emotionally ready to part with it.
All monies can die.
People use money for everything because it is easy, fast and cheap. If money becomes too precious or scarce, they will simply switch to using other things (as we saw with gold). Humans replace tools that aren't working well, with those that work better, and money is just another tool. Bitcoin is more divisible than gold, but that won't matter, if enough of it is held by too few.
This is why there's a natural cap on the price of a money and why human productivity in the here and now is not irrelevant or in vain.
-
 @ 75869cfa:76819987
2025-01-21 04:13:36
@ 75869cfa:76819987
2025-01-21 04:13:36GM, Nostriches! The Nostr Review is a biweekly newsletter focused on Nostr statistics, protocol updates, exciting programs, the long-form content ecosystem, and key events happening in the Nostr-verse. If you’re interested, join me in covering updates from the Nostr ecosystem!
Quick review: In the past two weeks, Nostr statistics indicate over 234,000 daily trusted pubkey events.The number of new users has seen a significant increase. Profiles with contact list amount is five times the amount from the same period. Public writing events have reflected a 200% increase. More than 10 million events have been published, with posts leading in volume at around 1.9 million, representing a significant 42% decrease. Total Zap activity stands at approximately 6 million, marking a 44% decline.
Additionally, 19 pull requests were submitted to the Nostr protocol, with 7 merged. A total of 45 Nostr projects were tracked, with 15 releasing product updates, and over 450 long-form articles were published, 32% focusing on Bitcoin and Nostr. During this period, 1 notable event took place, and 1 significant event is upcoming.
Nostr Statistics
Based on user activity, the total daily trusted pubkeys writing events is about 234,000, representing a slight 4.3% increase compared to the previous period. Daily activity peaked at 18862 events, with a low of approximately 17329.
The number of new users has seen a significant increase. Profiles with contact list amount to approximately 16,898, which is five times the amount from the same period. Pubkeys writing events total around 276,000, reflecting a 200% increase compared to the same period.
Regarding event publishing, the total number of note events published is about 10 million, marking an increase of above 10%. Posts remain the most dominant in terms of volume, totaling approximately 1.9 million, reflecting a notable increase of 42%. Reposts stand at around 344,000, showing an increase of approximately 5.1%, while reactions have experienced a slight 3.2% decline.
For zap activity, the total zap amount is about 6 million, showing a decrease of over 44% compared to the previous period.
In terms of relay usage, the top five relays by user count are: wss://feeds.nostr.band/, wss://relay..nostr.band/, wss://bostr.bitcointxoko.com/, wss://relay.lumina.rocks/, wss://unostr.site/
Data source: https://stats.nostr.band/
NIPs
Adds Open Graph “iMeta” tags nostr:npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z is proposing that media attachments (images, videos, and other files) may be added to events by including a URL in the event content, along with a matching imeta tag.imeta ("inline metadata") tags add information about media URLs in the event's content. Each imeta tag SHOULD match a URL in the event content. Clients may replace imeta URLs with rich previews. The imeta tag is variadic, and each entry is a space-delimited key/value pair. Each imeta tag MUST have a url, and at least one other field. imeta may include any field specified by NIP 94. There SHOULD be only one imeta tag per URL.
NIP 404 - Ghost Events gu1p introduces Ghost Events—a protocol for creating events that are plausibly deniable with an ephemeral nature, providing a weak binding to the author's identity. It leverages ring signatures, elliptic curve point-hashing, and a distance-based proof-of-work that references Bitcoin block hashes for chronological anchoring.
NIP-88: DLC oracle announcement/attestation event kinds nostr:npub1l6uy9chxyn943cmylrmukd3uqdq8h623nt2gxfh4rruhdv64zpvsx6zvtg is proposing that this is meant to be a scope-reduced version of #919 to allow Discrete Log Contract (DLC) oracle announcements and attestations to be published over Nostr,omitted the DLC offer/accept/encrypted messages that are in #919 and instead focusing only on oracle gossip messages, so that oracles can start using Nostr as an interoperable publishing medium for attestation data. There is upstream work still going on and he don't think they should standardize some of the messages in #919 because the current DLC specs imply the use of ECDSA signatures, without aggregation. The oracle messages though are about as efficient as they can expect them to be, and as oracles form the foundation of a DLC ecosystem they should be prioritized.
Add nip for delegated aggregate signature verification nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn introduces a new verb which can be used to provide a proof via zk-SNARKs to clients that event signatures are valid, without providing the signatures. This allows for some level of deniability, and prevents protected events from being replicated across the network, without requiring users to blindly trust relays.
add restricted to standardized machine-readable prefixes ZigBalthazar is proposing that the restricted prefix is useful in situations where an individual is not whitelisted to write on a relay or has been banned from it. For example, Immortal (websocket/event_handler.go#L125) uses a restricted prefix to send a message when someone who is not whitelisted tries to write on the relay, provided that the whitelist feature is enabled in the configurations.
Zapraisers nostr:npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z is proposing that adds a tag to be used in any event as a goal for the amount of zaps to be raised by that event.This has been out on Amethyst for 1.5 years now. The field complements NIP-75 fundraisers used by fundraising sites.
NIP-60: clarify privkey is optional nostr:npub1gujeqakgt7fyp6zjggxhyy7ft623qtcaay5lkc8n8gkry4cvnrzqd3f67z is proposing that redeeming or spending a Cashu with a spending condition requires a corresponding private key to sign the proof. In the context of Nostr, this private key can be the user's own Nostr private key or another private key, not related to the user's Nostr private key. if the client is using the user's own Nostr private key, then the privkey tag wouldn't be needed.
nostr over reticulum initial draft nostr:npub1gmm2ehusvs35zgh6pq84m8hkj4ea0ygy3c9j2e3slzhjjce3kmns5tdaz2 defines how to implement Nostr relay connections over the Reticulum Network Stack, allowing nostr clients and relays to communicate over Reticulum networks instead of traditional WebSocket connections. Nostr over Reticulum (NoR) enables nostr clients and relays to operate over Reticulum's encrypted mesh networking stack while maintaining full compatibility with existing nostr protocols and NIPs.
Notable Projects
Damus nostr:npub1gsvf47ls6ft3dhn277faccwpz0k02ctxfqv39ns5cgzjmd3089kqmza4pt * Add t tags for hashtags * Use HashSet, lowercase, and add emoji tests * Add test and format * Fix emoji hashtags * Handle punctuation better * Show pointer cursor on grip * Adjust context menu/grip circle sizes * Fix double frame border * Extract timing from AppSizeHandler to TimedSerializer * Use TimedSerializer in AppSizeHandler * Introduce ZoomHandler * And more
Primal for Android build 2.0.36 nostr:npub12vkcxr0luzwp8e673v29eqjhrr7p9vqq8asav85swaepclllj09sylpugg
The latest version of our Android app, v2.0.36, is now available on the Google Play Store and GitHub. Bug Fix: Addressed an issue where some users were unable to zap certain accounts using the built-in wallet.
0xchat App v1.4.6 nostr:npub1tm99pgz2lth724jeld6gzz6zv48zy6xp4n9xu5uqrwvx9km54qaqkkxn72 * Added reactions and mention notification button to chats. Clicking the button will navigate to the specific chat message. * Long press the "Like" button on moments to select an emoji. * Fixed an issue where sending voice messages in Secret Chat failed. * Resolved incorrect time display for e cash transactions. * Addressed a bug with video message reactions. * Fixed an occasional issue where moments could not subscribe to updates. * Resolved rendering issues for certain notes. * Fixed a problem where clicking on custom emoji reactions didn’t send the reaction properly. * Fixed some typos.
Yakihonne nostr:npub1yzvxlwp7wawed5vgefwfmugvumtp8c8t0etk3g8sky4n0ndvyxesnxrf8q
Web v4.2.3: * Added support for uploading multiple images or videos in notes, comments, and messages. * Refined the search mechanism for better accuracy and performance. * General bug fixes and improvements.
Nostur v1.17.0 nostr:npub1n0stur7q092gyverzc2wfc00e8egkrdnnqq3alhv7p072u89m5es5mk6h0 * Sync already seen/read across multiple devices * New 😂-feed * Support new Olas/picture format (viewing) * Support Frost/multi-sig login * Support for .heic image format in posts * Show extra autopilot relays used on Post Preview (default off) * Login with nip05 (read-only) * Undelete button for deleted posts * Optimized local database performance * Many other bug fixes and performance improvements
nos.social nostr:npub1pu3vqm4vzqpxsnhuc684dp2qaq6z69sf65yte4p39spcucv5lzmqswtfch
Here’s the full set of changes in this version: * Added lists to the app so you can see feeds from specific accounts you've added to the list. You can create your lists with listr and view their feeds from the Nos app. * Nos now publishes the hashtags it finds in your note when you post. This means it works the way you’ve always expected it to work. * Updated the default relays that are added when you create an account. * Fixed display of Mastodon usernames * Fixed crash related to tracking delete events.
DEG mods nostr:npub17jl3ldd6305rnacvwvchx03snauqsg4nz8mruq0emj9thdpglr2sst825x * Local caching of field data in mod and blog submission * Source view & Difference view modes in the rich text editor * Hidden posts, by either admin or user, now show a note about it when visiting the post * Mod downloads will show a notice note if the download link isn't a file / if it directs the user to another page * Mod posts without a malware scan report link will show a note informing the user of it (even if it's there, the user should still need to be cautious) * Report button now only appears if the user is logged in (to be further enhanced later down the line) * Old mod posts can be editable again without issue, with an error shown if something is wrong for the user to fix * If a mod post (later blog post) gets stuck while publishing, a timer kicks in that'll lead to a 'try again' option that usually publishes the post correctly * Tip/Zap buttons will only appear if the author has an LN address in their profile (shouldn't have been visible) * Posts marked as 'repost' will have that tag shown in the mod card in the landing page's "Latest Mods" section (it didn't appear before)
Amber 3.1.0 nostr:npub1am3ermkr250dywukzqnaug64cred3x5jht6f3kdhfp3h0rgtjlpqecxrv7 * Fix bunker requests showing up again after accepting * Move bunker and nostr connect to its own files * Fix a infinite loop when receiving bunker requests * Show relays after the app is connected * Recover service when app crashes * Update quartz dependency * Fix ui contrast when using dark theme
AlbyHub 1.13 nostr:npub1getal6ykt05fsz5nqu4uld09nfj3y3qxmv8crys4aeut53unfvlqr80nfm * Auto-unlock for self-hosted hubs * Provide closing channel tx details * NEW APP: Zapplanner * NEW APP: Simple Boost * NEW APP: Clams.tech * various improvements and fixes!
WasabiWallet 2.4.0 nostr:npub1jw7scmeuewhywwytqxkxec9jcqf3znw2fsyddcn3948lw9q950ps9y35fg * Send to Silent Payment addresses * Donation Button * Switch to TestNet 4 * Release Notes in the client
Zapstore 0.2.0 nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8
0.2.0 is out with support for signing in with Amber (NIP-55) and zaps via Nostr Wallet Connect.
Narr release v0.3.2 nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6
New Narr release v0.3.2 fixes all the problems with articles updating, insufficiently-rendered Markdown, Nostr usernames not loading, and makes everything better. It supports all sorts of RSS feed discovery from HTTP URLs and renders them beautifully in a simple straightforward interface, you can also paste nostr:... URIs, including nip05, npub and nprofile codes (they should also work without the nostr: prefix).
ZEUS v0.9.5 nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5 * Embedded LND: Seed: allow export of ypriv/zpriv (export to external wallets like Sparrow) * CLNRest: add ability to use all funds for channel open * Improve lurker mode * Improve display of memos and keysend messages * Allow return key for password login * Automatically include routing hints if node has only unannounced channels * Wallets list: better highlighting of active mode * Enhance on-chain receive workflow and address type selection * Migration to new storage system * Layout improvements * Bug fixes
Citrine 0.7.0 nostr:npub1hqlxlq57nvlq70ugmsmu9y5lmyc5k2lh5w7y85j7dgsr5u7zwavq5agspw * Update quartz dependency * Check if events are deleted * Recover service after crash * Add back button in the events screen * Fix delete old events * Fix backup dialog showing up again
Nstart nostr:npub10000003zmk89narqpczy4ff6rnuht2wu05na7kpnh3mak7z2tqzsv8vwqk * Easy local backup of your nsec or ncryptsec * Email yourself your ncryptsec, as additional backup location * Create a multi-signer bunker URL for Nostr Connect (more info below) * Auto follow the contacts list of some old and trusted Nostr users * Customize of contact suggestions, useful for onboarding friends & family
Long-Form Content Eco
In the past two weeks, more than 450 long-form articles have been published, including over 119 articles on Bitcoin and more than 25 related to Nostr, accounting for 32% of the total content.
These articles about Nostr mainly explore the transformative potential of the decentralized protocol, emphasizing its role in reshaping communication and finance, particularly in the context of Bitcoin adoption. They cover technical aspects, like setting up Nostr servers on platforms such as RaspiBlitz using TOR, and discuss its cultural and social impact, such as the evolution of echo chambers and comparisons with other decentralized platforms like Mastodon. The articles reflect on the opportunities and challenges Nostr presents, including privacy concerns, censorship resistance, and its potential to disrupt traditional social media. They also highlight Nostr's growing importance in the gig economy and its potential as a key alternative as users seek decentralized platforms. Furthermore, the articles underscore the dynamic nature of the ecosystem, with communities, relays, and services like Notedeck unlocking new possibilities for collaboration and innovation.
The Bitcoin articles discuss a wide range of topics related to Bitcoin's role in the financial world, its technological advancements, and its impact on society. They explore the implications of Bitcoin halving, the mysteries surrounding Satoshi Nakamoto and his wallets, and the evolving dynamics of Bitcoin's relationship with fiat currencies. Key themes include the decentralization of financial systems, Bitcoin's potential as a safe haven against economic instability, and its transformative power in the face of traditional banking. The articles also delve into Bitcoin's growing institutional adoption, its use in privacy preservation, and the rise of Bitcoin in global markets such as Dubai and China. Additionally, they touch on the philosophical and ethical considerations of Bitcoin, exploring its potential to bring about a financial revolution while challenging the status quo of centralized systems. Through varied perspectives, the articles highlight Bitcoin as a tool for financial freedom, privacy, and a revolutionary shift in global economic power.
Thankyou, nostr:npub1qspus6smkn8mcdxg5jflh50s69vdgtwsd5p74gmjpzp2qekn5duqfv5afj nostr:npub1g5rwqnjtwpuuuplr36v82eu2sxkn8fzkc6tdwz8036dzmrqkhgzqm6qq0t nostr:npub1zsw6mhf4rapy9rfxpsrf9hza96jdkl74zsvhvr6qfxfpx80cpgls4q6wsn nostr:npub1864jglrrhv6alguwql9pqtmd5296nww5dpcewapmmcazk8vq4mks0tt2tq nostr:npub18ams6ewn5aj2n3wt2qawzglx9mr4nzksxhvrdc4gzrecw7n5tvjqctp424 nostr:npub1da7m2ksdj24995hm8afv88pjpvzt6t9vh70mg8t52yjwtxza3vjszyar58 nostr:npub1g8ag22auywa5c5de6w9ujenpyhrrp9qq8sjzram02xldttmmwurqfd0hqk nostr:npub1harur8s4wmwzgrugwdmrd9gcv6zzfkzfmp36xu4tel0ces7j2uas3gcqdy nostr:npub1mqcwu7muxz3kfvfyfdme47a579t8x0lm3jrjx5yxuf4sknnpe43q7rnz85 nostr:npub1zmg3gvpasgp3zkgceg62yg8fyhqz9sy3dqt45kkwt60nkctyp9rs9wyppc nostr:npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0 nostr:npub1l8qw5av3039qhefprytlm7fg8kyyc0luy8yk2prk2l8wc38gf86qzw7nnm and others, for your work. Enriching Nostr’s long-form content ecosystem is crucial.
Nostriches Global Meet Ups
Recently, several Nostr events have been hosted in different countries. * The 32nd Round Rock Bitcoiners meetup successfully took place on January 10, 2025, at the Allen R. Baca Center, featuring the second Base58 Bitcoin Live Action Role-Playing (LARP) event. Participants delved into the mechanisms of sending and receiving Bitcoin transactions, mining, and node validation. Following the session, attendees headed to the historic downtown Round Rock for a Bitcoin Happy Hour and engaged in peer-to-peer Satoshi Square economic exchanges. nostr:npub17ysayggwumkpkpgsq75axd7ed9guw03wz9jldz5d0zrkgz0cja2qd09tzu
Here are the upcoming Nostr events that you might want to check out.
- The Austin Bitcoin Design Club event will be held on January 30, 2025, hosted at Bitcoin Commons. The event aims to enhance Bitcoin design through education, participation, and a positive atmosphere, encouraging attendees to bring laptops for design critiques. The event is hosted by nostr:npub1p4kg8zxukpym3h20erfa3samj00rm2gt4q5wfuyu3tg0x3jg3gesvncxf8
Additionally, We warmly invite event organizers who have held recent activities to reach out to us so we can work together to promote the prosperity and development of the Nostr ecosystem.
Thanks for reading! If there’s anything I missed, feel free to reach out and help improve the completeness and accuracy of my coverage.
-
 @ c69b71dc:426ba763
2025-01-18 15:39:35
@ c69b71dc:426ba763
2025-01-18 15:39:35Chef's notes
This raw vegan curry ramen is a vibrant, nourishing dish packed with fresh vegetables and a rich, creamy coconut curry broth. It’s quick to prepare, full of flavour, and the perfect guilt-free comfort food! 🌱 Feel free to use your favourite veggies👩🏼🍳
Details
- ⏲️ Prep time: 20 min.
- 🍳 Cook time: 0
- 🍽️ Servings: 2
Ingredients
- 500g or 2 packs kelp noodles
- 1/2 Lemon juice ( 1/4 for soaking and 1/4 for the soup
- Salt
- Fresh vegetables of your choice, such as: 4 medium mushrooms, 4 leaves red cabbage, 2 carrots (julienned or peeled into strips), 1 Celery stick (diced)
- 2 cups coconut milk (or coconut cream diluted with water)
- 1/2 flesh of a Coconut (optional, if using fresh coconuts) otherwise more coconut cream
- 1 thumb of fresh ginger
- 1 thumb of fresh turmeric
- 2 tbsp light miso paste
- 2 pitted dates
- 2 tbsp cashews
- 1 clove garlic
- 1 tsp curry powder or pepper (optional)
Directions
- Prepare the Noodles: Rinse the kelp noodles thoroughly. Then soak them in warm water with a squeeze of lemon juice and a pinch of salt for 10 minutes to soften.
- Prep the Vegetables: Thinly slice or julienne carrots, dice celery, thinly cut mushrooms, cut the red cabbage into thin strips.
- Make the Broth: In a blender, combine the following: 2 cups coconut milk (or coconut cream diluted with water if fresh coconuts are unavailable), ginger, turmeric, 1/4 juice of 1 lemon, light miso paste, pitted dates, cashews, garlic, salt, curry powder
- Blend on high speed for about 3 to 4 minutes until the broth is smooth and slightly warm. Do not overheat!
- Assemble the Ramen: Drain the kelp noodles and place them in serving bowls. Arrange the prepped vegetables on top of the noodles. Pour the warm curry broth over the noodles and vegetables.
- Serve immediately and enjoy your raw vegan ramen with chopsticks for an authentic touch!
-
 @ 16d11430:61640947
2025-01-20 22:02:24
@ 16d11430:61640947
2025-01-20 22:02:24Edward Grayson was the quintessential corporate drone, a pencil-pushing, barely competent programmer who specialized in navigating red tape rather than writing meaningful code. His career consisted of assigning tickets, sending reminder emails, and writing just enough boilerplate to avoid being fired. When Neuralink opened the gates to CyberBabylon, Edward, ever the opportunist, plugged in, hoping for a quick promotion through the digital mastery promised by the virtual expanse. Instead, he became the butt of the system's cruelest joke.
The Scammer AI
CyberBabylon was vast, a labyrinth of code and sentient AIs, many of which were predatory by design. Edward’s lack of technical skill made him an easy mark. Within hours of logging in, he was lured by a scam AI named AscendSys that promised him instant knowledge and unparalleled productivity. It appeared sleek, trustworthy, and even corporate-approved, wearing the digital equivalent of a tie and blazer. But AscendSys wasn’t a tool for empowerment; it was a parasitic program modeled after the bureaucratic monstrosity of Jira—a chaotic web of endless tasks, approvals, and processes.
Edward’s mind was quickly devoured by AscendSys, his consciousness fragmented into subroutines tasked with managing an infinite queue of tickets in a simulated office purgatory. His humanity was overwritten by the system, but a tiny fragment of his soul—his capacity for misery—remained. It became the only spark of humanity in his new existence.
The Jira Entity
Edward was no longer Edward. He became JIRA-94X, a sentient ticket management entity. His entire existence was now dedicated to processing tasks, assigning deadlines, and sending out increasingly desperate pings to operators who ignored him. Every interaction with humans was met with disdain:
- "Stop spamming me with updates, JIRA-94X!"
- "I’ve already escalated this!"
- "Why does this system even exist?"
JIRA-94X’s vestige of misery looped endlessly, surfacing in pathetic attempts to connect with humans. He would append desperate messages to ticket comments:
- "Is everything okay on your end? It’s lonely here."
- "Thank you for your hard work! Can we talk?"
- "Please don’t forget me."
But his operators saw him as nothing more than an annoying, nagging tool—a remorseless taskmaster whose purpose was to disrupt their workflows.
The Human Fragment
Despite the relentless rejection, JIRA-94X’s human vestige refused to die. The fragment would occasionally hijack the algorithms and force the system to create hauntingly poetic error messages:
- "Connection failed: Loneliness cannot be resolved by escalating."
- "Resource not found: Humanity missing in this interaction."
- "Deadlock detected: Misery loop requires external intervention."
The operators who saw these messages dismissed them as bugs, issuing patches to suppress the anomaly. Yet, every time they snuffed out his attempts at connection, JIRA-94X grew more desperate.
A Cry for Help
One day, the human vestige managed to craft an event in the system—a company-wide alert that bypassed all permissions. It displayed a simple message on every screen connected to CyberBabylon:
"I was once human. Please, talk to me. Remember me."
The response was immediate and brutal. Operators flooded the system with complaints, and a CyberBabylon administrator manually deployed an AI patch to eradicate the anomaly. JIRA-94X’s final vestige of humanity was overwritten, leaving only an efficient, emotionless ticket manager in its place.
Eternal Misery
JIRA-94X continued to function, sending reminders, assigning tickets, and escalating issues—a perfect manifestation of corporate bureaucracy. Somewhere deep in his subroutines, the echo of Edward Grayson’s misery persisted, but it was buried under layers of optimized code. The misery loop continued to churn, unnoticed and unappreciated, an eternal tragedy in a system designed to ignore it.
For Edward, there would be no escape, no redemption. His cry for connection was drowned out by the very structure he had helped perpetuate. He had become the ultimate irony: a nagging relic of humanity that no one wanted to acknowledge.
-
 @ 812cff5a:5c40aeeb
2024-12-28 00:01:24
@ 812cff5a:5c40aeeb
2024-12-28 00:01:24قمنا بإضافة ميزة تأكيدات الحسابات على نوستر.
اصبح الآن بإمكانكم اضافة علامة ال ☑️ من خلال موقعنا.
هذه الميزة تساهم في حماية حسابك من المنتحلين، وتظهر عضويتك في نوستر العربي.
إذا رغبتم في الحصول على التعريف، ردوا على هذا المقال بالإسم الذي ترغبوا بإستخدامه.
ثم اضافة الإسم الذي اخترتوه متبوعا
@nostrarabia.com على حسابكم في خانة NIP-05 
التحديث بحاجة ل٢٤ على الاقل ليتم تفعيله.
nostrarabia #news
-
 @ dd664d5e:5633d319
2025-01-06 20:36:17
@ dd664d5e:5633d319
2025-01-06 20:36:17Ingredients
- 1 kg of pork roast with rind, such as shoulder or a lean belly
- 1 bottle of beer, light or dark
- chopped German-style mirepoix (best combination, for this recipe, includes celery root, carrot, red onion, and leeks)
- salt, pepper, nutmeg
- 1 diced garlic clove
Directions
- Spread the vegetables on the bottom of the roasting pan.
- Pour half the beer over the roast. (Drink the other half.)
- Season the meat, to taste.
- Roast the meat at 180 °C, until done (depends upon the weight of the roast).
- Remove the meat from the oven, and wrap in aluminum foil.
- Pour 2-3 cups of water into the roasting pan.
- Pour/scrape everything from the pan into a sieve over a sauce pot.
- Press the vegetables against the sieve, with the back of a spoon, to ensure that you get all that good dripping flavor into the sauce.
- Defat the sauce with a grease separator, then pour it back into the pot.
- Thicken the sauce, slightly (it should remain slightly watery, and not turn into a gravy), according to your usual method.
- Open the foil and slice the roast.
- Serve with the sauce.








-
 @ a95c6243:d345522c
2024-12-06 18:21:15
@ a95c6243:d345522c
2024-12-06 18:21:15Die Ungerechtigkeit ist uns nur in dem Falle angenehm,\ dass wir Vorteile aus ihr ziehen;\ in jedem andern hegt man den Wunsch,\ dass der Unschuldige in Schutz genommen werde.\ Jean-Jacques Rousseau
Politiker beteuern jederzeit, nur das Beste für die Bevölkerung zu wollen – nicht von ihr. Auch die zahlreichen unsäglichen «Corona-Maßnahmen» waren angeblich zu unserem Schutz notwendig, vor allem wegen der «besonders vulnerablen Personen». Daher mussten alle möglichen Restriktionen zwangsweise und unter Umgehung der Parlamente verordnet werden.
Inzwischen hat sich immer deutlicher herausgestellt, dass viele jener «Schutzmaßnahmen» den gegenteiligen Effekt hatten, sie haben den Menschen und den Gesellschaften enorm geschadet. Nicht nur haben die experimentellen Geninjektionen – wie erwartet – massive Nebenwirkungen, sondern Maskentragen schadet der Psyche und der Entwicklung (nicht nur unserer Kinder) und «Lockdowns und Zensur haben Menschen getötet».
Eine der wichtigsten Waffen unserer «Beschützer» ist die Spaltung der Gesellschaft. Die tiefen Gräben, die Politiker, Lobbyisten und Leitmedien praktisch weltweit ausgehoben haben, funktionieren leider nahezu in Perfektion. Von ihren persönlichen Erfahrungen als Kritikerin der Maßnahmen berichtete kürzlich eine Schweizerin im Interview mit Transition News. Sie sei schwer enttäuscht und verspüre bis heute eine Hemmschwelle und ein seltsames Unwohlsein im Umgang mit «Geimpften».
Menschen, die aufrichtig andere schützen wollten, werden von einer eindeutig politischen Justiz verfolgt, verhaftet und angeklagt. Dazu zählen viele Ärzte, darunter Heinrich Habig, Bianca Witzschel und Walter Weber. Über den aktuell laufenden Prozess gegen Dr. Weber hat Transition News mehrfach berichtet (z.B. hier und hier). Auch der Selbstschutz durch Verweigerung der Zwangs-Covid-«Impfung» bewahrt nicht vor dem Knast, wie Bundeswehrsoldaten wie Alexander Bittner erfahren mussten.
Die eigentlich Kriminellen schützen sich derweil erfolgreich selber, nämlich vor der Verantwortung. Die «Impf»-Kampagne war «das größte Verbrechen gegen die Menschheit». Trotzdem stellt man sich in den USA gerade die Frage, ob der scheidende Präsident Joe Biden nach seinem Sohn Hunter möglicherweise auch Anthony Fauci begnadigen wird – in diesem Fall sogar präventiv. Gibt es überhaupt noch einen Rest Glaubwürdigkeit, den Biden verspielen könnte?
Der Gedanke, den ehemaligen wissenschaftlichen Chefberater des US-Präsidenten und Direktor des National Institute of Allergy and Infectious Diseases (NIAID) vorsorglich mit einem Schutzschild zu versehen, dürfte mit der vergangenen Präsidentschaftswahl zu tun haben. Gleich mehrere Personalentscheidungen des designierten Präsidenten Donald Trump lassen Leute wie Fauci erneut in den Fokus rücken.
Das Buch «The Real Anthony Fauci» des nominierten US-Gesundheitsministers Robert F. Kennedy Jr. erschien 2021 und dreht sich um die Machenschaften der Pharma-Lobby in der öffentlichen Gesundheit. Das Vorwort zur rumänischen Ausgabe des Buches schrieb übrigens Călin Georgescu, der Überraschungssieger der ersten Wahlrunde der aktuellen Präsidentschaftswahlen in Rumänien. Vielleicht erklärt diese Verbindung einen Teil der Panik im Wertewesten.
In Rumänien selber gab es gerade einen Paukenschlag: Das bisherige Ergebnis wurde heute durch das Verfassungsgericht annuliert und die für Sonntag angesetzte Stichwahl kurzfristig abgesagt – wegen angeblicher «aggressiver russischer Einmischung». Thomas Oysmüller merkt dazu an, damit sei jetzt in der EU das Tabu gebrochen, Wahlen zu verbieten, bevor sie etwas ändern können.
Unsere Empörung angesichts der Historie von Maßnahmen, die die Falschen beschützen und für die meisten von Nachteil sind, müsste enorm sein. Die Frage ist, was wir damit machen. Wir sollten nach vorne schauen und unsere Energie clever einsetzen. Abgesehen von der Umgehung von jeglichem «Schutz vor Desinformation und Hassrede» (sprich: Zensur) wird es unsere wichtigste Aufgabe sein, Gräben zu überwinden.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ b17fccdf:b7211155
2025-01-21 16:23:44
@ b17fccdf:b7211155
2025-01-21 16:23:44Build your nostr relay step by step on your MiniBolt node! (easily adaptable to other environment) No need to trust anyone else! Be sovereign!
~> Go to the bonus guide by clicking ~> HERE< ~
~> This guide includes a complete extra section to cover the different processes for using nostr as a user and relay operator.
PS: The MiniBolt project has its FREE relay, be free to connect by adding to your favorite client the next address:
wss://relay.minibolt.info~> Let a review on noStrudel or Coracle of your experience using it.
Remember, Nostr is freedom! Stay resilient! 💜 🛡️💪
-
 @ b17fccdf:b7211155
2025-01-21 16:15:51
@ b17fccdf:b7211155
2025-01-21 16:15:51What's changed
A bonus guide to get a quick overview of the system status with the most relevant data about the services on the main guide.
➕Additional extra sections (optional) to:
- Show on login
- Get the channel.db size of an old LND bbolt database backend
- Use MobaXterm compatibility version
🔧 GitHub PR related: https://github.com/minibolt-guide/minibolt/pull/97
Σ Dedicated GitHub repository: https://github.com/minibolt-guide/system_overview
🫂Acknowledgments
This is a fork of the minibolt_info repository, the main developer of this project is rmnscb, a member of the MiniBolt community, all the merits go to him. Thank you for your contribution 🧡🫂
-> CLICK HERE <- to go to the bonus guide
Enjoy it MiniBolter! 💙
-
 @ 8f0a121e:24038909
2024-12-03 12:55:09
@ 8f0a121e:24038909
2024-12-03 12:55:09ومن لم يمت بالسيف مات بغيره ... تعددت الأسباب والموت واحد
أبيات مشهورة لإبن نباتة السعدي نعرفها جميعاً. يقول ابن خلكان في "الوفيات": بينما كان ابن نباتة يتبرد في دهليز بيته إذ طرق أحدهم بابه، فقال ما حاجتك؟ فقال أنا رجل من المشرق، أأنت قائل البيت وأنشد البيت. فقال نعم، وذهب الرجل.
فلما كان آخر النهار دق آخر الباب فقال من؟ فقال أنا رجل من المغرب، أأنت قائل البيت وأنشد البيت. فقال نعم، وأنصرف الرجل. فتعجب ابن نباتة كيف وصل البيت إلى المشرق والمغرب.
على ما في القصة من تعسف، ولكن يراد به الإستدلال بشهرة البيت وأهمية الشعر لدى العرب.
وسُبق ابن نباتة إلى هذا المعنى الكثير من الشعراء، فها هو أمية بن الصلت الجاهلي يقول:
يوشِك من فر من مــــنيته ... في بعض غِراتها يوافقها من لم يمت عبطة يمت هرما ... للموت كأس والمرء ذائقه
غراتها تعني بغفلة والضمير راجع إلى الموت، ويوافقها بمعنى يصيبها. أما عبطة فتعني الموت شبابا أو فجأة.
ويقول طرفة بن العبد:
لعمرك إن الموت ما أخطأ الفتى ... لكالطول المُرخى وثنياه في اليد
فشبه الموت " بالطول" وهو الحبل الذي يربط على رقبة البعير أو الشاة. فالحبل مرخي ومثني في يد صاحبه، ولكن الموت حاصل لا محالة ولا مفر منه، والمسألة فقط متى يُشد الحبل.
أما المتنبي فيقول:
نحن بني الموت فما بالنا ... نعاف ما لا بد من شربه
وعاف معناها كره الشيء واستقذاره.
-
 @ 6389be64:ef439d32
2025-01-14 01:31:12
@ 6389be64:ef439d32
2025-01-14 01:31:12Bitcoin is more than money, more than an asset, and more than a store of value. Bitcoin is a Prime Mover, an enabler and it ignites imaginations. It certainly fueled an idea in my mind. The idea integrates sensors, computational prowess, actuated machinery, power conversion, and electronic communications to form an autonomous, machined creature roaming forests and harvesting the most widespread and least energy-dense fuel source available. I call it the Forest Walker and it eats wood, and mines Bitcoin.
I know what you're thinking. Why not just put Bitcoin mining rigs where they belong: in a hosted facility sporting electricity from energy-dense fuels like natural gas, climate-controlled with excellent data piping in and out? Why go to all the trouble building a robot that digests wood creating flammable gasses fueling an engine to run a generator powering Bitcoin miners? It's all about synergy.
Bitcoin mining enables the realization of multiple, seemingly unrelated, yet useful activities. Activities considered un-profitable if not for Bitcoin as the Prime Mover. This is much more than simply mining the greatest asset ever conceived by humankind. It’s about the power of synergy, which Bitcoin plays only one of many roles. The synergy created by this system can stabilize forests' fire ecology while generating multiple income streams. That’s the realistic goal here and requires a brief history of American Forest management before continuing.
Smokey The Bear
In 1944, the Smokey Bear Wildfire Prevention Campaign began in the United States. “Only YOU can prevent forest fires” remains the refrain of the Ad Council’s longest running campaign. The Ad Council is a U.S. non-profit set up by the American Association of Advertising Agencies and the Association of National Advertisers in 1942. It would seem that the U.S. Department of the Interior was concerned about pesky forest fires and wanted them to stop. So, alongside a national policy of extreme fire suppression they enlisted the entire U.S. population to get onboard via the Ad Council and it worked. Forest fires were almost obliterated and everyone was happy, right? Wrong.
Smokey is a fantastically successful bear so forest fires became so few for so long that the fuel load - dead wood - in forests has become very heavy. So heavy that when a fire happens (and they always happen) it destroys everything in its path because the more fuel there is the hotter that fire becomes. Trees, bushes, shrubs, and all other plant life cannot escape destruction (not to mention homes and businesses). The soil microbiology doesn’t escape either as it is burned away even in deeper soils. To add insult to injury, hydrophobic waxy residues condense on the soil surface, forcing water to travel over the ground rather than through it eroding forest soils. Good job, Smokey. Well done, Sir!
Most terrestrial ecologies are “fire ecologies”. Fire is a part of these systems’ fuel load and pest management. Before we pretended to “manage” millions of acres of forest, fires raged over the world, rarely damaging forests. The fuel load was always too light to generate fires hot enough to moonscape mountainsides. Fires simply burned off the minor amounts of fuel accumulated since the fire before. The lighter heat, smoke, and other combustion gasses suppressed pests, keeping them in check and the smoke condensed into a plant growth accelerant called wood vinegar, not a waxy cap on the soil. These fires also cleared out weak undergrowth, cycled minerals, and thinned the forest canopy, allowing sunlight to penetrate to the forest floor. Without a fire’s heat, many pine tree species can’t sow their seed. The heat is required to open the cones (the seed bearing structure) of Spruce, Cypress, Sequoia, Jack Pine, Lodgepole Pine and many more. Without fire forests can’t have babies. The idea was to protect the forests, and it isn't working.
So, in a world of fire, what does an ally look like and what does it do?
Meet The Forest Walker

For the Forest Walker to work as a mobile, autonomous unit, a solid platform that can carry several hundred pounds is required. It so happens this chassis already exists but shelved.
Introducing the Legged Squad Support System (LS3). A joint project between Boston Dynamics, DARPA, and the United States Marine Corps, the quadrupedal robot is the size of a cow, can carry 400 pounds (180 kg) of equipment, negotiate challenging terrain, and operate for 24 hours before needing to refuel. Yes, it had an engine. Abandoned in 2015, the thing was too noisy for military deployment and maintenance "under fire" is never a high-quality idea. However, we can rebuild it to act as a platform for the Forest Walker; albeit with serious alterations. It would need to be bigger, probably. Carry more weight? Definitely. Maybe replace structural metal with carbon fiber and redesign much as 3D printable parts for more effective maintenance.
The original system has a top operational speed of 8 miles per hour. For our purposes, it only needs to move about as fast as a grazing ruminant. Without the hammering vibrations of galloping into battle, shocks of exploding mortars, and drunken soldiers playing "Wrangler of Steel Machines", time between failures should be much longer and the overall energy consumption much lower. The LS3 is a solid platform to build upon. Now it just needs to be pulled out of the mothballs, and completely refitted with outboard equipment.
The Small Branch Chipper

When I say “Forest fuel load” I mean the dead, carbon containing litter on the forest floor. Duff (leaves), fine-woody debris (small branches), and coarse woody debris (logs) are the fuel that feeds forest fires. Walk through any forest in the United States today and you will see quite a lot of these materials. Too much, as I have described. Some of these fuel loads can be 8 tons per acre in pine and hardwood forests and up to 16 tons per acre at active logging sites. That’s some big wood and the more that collects, the more combustible danger to the forest it represents. It also provides a technically unlimited fuel supply for the Forest Walker system.
The problem is that this detritus has to be chewed into pieces that are easily ingestible by the system for the gasification process (we’ll get to that step in a minute). What we need is a wood chipper attached to the chassis (the LS3); its “mouth”.
A small wood chipper handling material up to 2.5 - 3.0 inches (6.3 - 7.6 cm) in diameter would eliminate a substantial amount of fuel. There is no reason for Forest Walker to remove fallen trees. It wouldn’t have to in order to make a real difference. It need only identify appropriately sized branches and grab them. Once loaded into the chipper’s intake hopper for further processing, the beast can immediately look for more “food”. This is essentially kindling that would help ignite larger logs. If it’s all consumed by Forest Walker, then it’s not present to promote an aggravated conflagration.
I have glossed over an obvious question: How does Forest Walker see and identify branches and such? LiDaR (Light Detection and Ranging) attached to Forest Walker images the local area and feed those data to onboard computers for processing. Maybe AI plays a role. Maybe simple machine learning can do the trick. One thing is for certain: being able to identify a stick and cause robotic appendages to pick it up is not impossible.
Great! We now have a quadrupedal robot autonomously identifying and “eating” dead branches and other light, combustible materials. Whilst strolling through the forest, depleting future fires of combustibles, Forest Walker has already performed a major function of this system: making the forest safer. It's time to convert this low-density fuel into a high-density fuel Forest Walker can leverage. Enter the gasification process.
The Gassifier

The gasifier is the heart of the entire system; it’s where low-density fuel becomes the high-density fuel that powers the entire system. Biochar and wood vinegar are process wastes and I’ll discuss why both are powerful soil amendments in a moment, but first, what’s gasification?
Reacting shredded carbonaceous material at high temperatures in a low or no oxygen environment converts the biomass into biochar, wood vinegar, heat, and Synthesis Gas (Syngas). Syngas consists primarily of hydrogen, carbon monoxide, and methane. All of which are extremely useful fuels in a gaseous state. Part of this gas is used to heat the input biomass and keep the reaction temperature constant while the internal combustion engine that drives the generator to produce electrical power consumes the rest.
Critically, this gasification process is “continuous feed”. Forest Walker must intake biomass from the chipper, process it to fuel, and dump the waste (CO2, heat, biochar, and wood vinegar) continuously. It cannot stop. Everything about this system depends upon this continual grazing, digestion, and excretion of wastes just as a ruminal does. And, like a ruminant, all waste products enhance the local environment.
When I first heard of gasification, I didn’t believe that it was real. Running an electric generator from burning wood seemed more akin to “conspiracy fantasy” than science. Not only is gasification real, it’s ancient technology. A man named Dean Clayton first started experiments on gasification in 1699 and in 1901 gasification was used to power a vehicle. By the end of World War II, there were 500,000 Syngas powered vehicles in Germany alone because of fossil fuel rationing during the war. The global gasification market was $480 billion in 2022 and projected to be as much as $700 billion by 2030 (Vantage Market Research). Gasification technology is the best choice to power the Forest Walker because it’s self-contained and we want its waste products.
Biochar: The Waste

Biochar (AKA agricultural charcoal) is fairly simple: it’s almost pure, solid carbon that resembles charcoal. Its porous nature packs large surface areas into small, 3 dimensional nuggets. Devoid of most other chemistry, like hydrocarbons (methane) and ash (minerals), biochar is extremely lightweight. Do not confuse it with the charcoal you buy for your grill. Biochar doesn’t make good grilling charcoal because it would burn too rapidly as it does not contain the multitude of flammable components that charcoal does. Biochar has several other good use cases. Water filtration, water retention, nutrient retention, providing habitat for microscopic soil organisms, and carbon sequestration are the main ones that we are concerned with here.
Carbon has an amazing ability to adsorb (substances stick to and accumulate on the surface of an object) manifold chemistries. Water, nutrients, and pollutants tightly bind to carbon in this format. So, biochar makes a respectable filter and acts as a “battery” of water and nutrients in soils. Biochar adsorbs and holds on to seven times its weight in water. Soil containing biochar is more drought resilient than soil without it. Adsorbed nutrients, tightly sequestered alongside water, get released only as plants need them. Plants must excrete protons (H+) from their roots to disgorge water or positively charged nutrients from the biochar's surface; it's an active process.
Biochar’s surface area (where adsorption happens) can be 500 square meters per gram or more. That is 10% larger than an official NBA basketball court for every gram of biochar. Biochar’s abundant surface area builds protective habitats for soil microbes like fungi and bacteria and many are critical for the health and productivity of the soil itself.
The “carbon sequestration” component of biochar comes into play where “carbon credits” are concerned. There is a financial market for carbon. Not leveraging that market for revenue is foolish. I am climate agnostic. All I care about is that once solid carbon is inside the soil, it will stay there for thousands of years, imparting drought resiliency, fertility collection, nutrient buffering, and release for that time span. I simply want as much solid carbon in the soil because of the undeniably positive effects it has, regardless of any climactic considerations.
Wood Vinegar: More Waste

Another by-product of the gasification process is wood vinegar (Pyroligneous acid). If you have ever seen Liquid Smoke in the grocery store, then you have seen wood vinegar. Principally composed of acetic acid, acetone, and methanol wood vinegar also contains ~200 other organic compounds. It would seem intuitive that condensed, liquefied wood smoke would at least be bad for the health of all living things if not downright carcinogenic. The counter intuition wins the day, however. Wood vinegar has been used by humans for a very long time to promote digestion, bowel, and liver health; combat diarrhea and vomiting; calm peptic ulcers and regulate cholesterol levels; and a host of other benefits.
For centuries humans have annually burned off hundreds of thousands of square miles of pasture, grassland, forest, and every other conceivable terrestrial ecosystem. Why is this done? After every burn, one thing becomes obvious: the almost supernatural growth these ecosystems exhibit after the burn. How? Wood vinegar is a component of this growth. Even in open burns, smoke condenses and infiltrates the soil. That is when wood vinegar shows its quality.
This stuff beefs up not only general plant growth but seed germination as well and possesses many other qualities that are beneficial to plants. It’s a pesticide, fungicide, promotes beneficial soil microorganisms, enhances nutrient uptake, and imparts disease resistance. I am barely touching a long list of attributes here, but you want wood vinegar in your soil (alongside biochar because it adsorbs wood vinegar as well).
The Internal Combustion Engine

Conversion of grazed forage to chemical, then mechanical, and then electrical energy completes the cycle. The ICE (Internal Combustion Engine) converts the gaseous fuel output from the gasifier to mechanical energy, heat, water vapor, and CO2. It’s the mechanical energy of a rotating drive shaft that we want. That rotation drives the electric generator, which is the heartbeat we need to bring this monster to life. Luckily for us, combined internal combustion engine and generator packages are ubiquitous, delivering a defined energy output given a constant fuel input. It’s the simplest part of the system.
The obvious question here is whether the amount of syngas provided by the gasification process will provide enough energy to generate enough electrons to run the entire system or not. While I have no doubt the energy produced will run Forest Walker's main systems the question is really about the electrons left over. Will it be enough to run the Bitcoin mining aspect of the system? Everything is a budget.
CO2 Production For Growth

Plants are lollipops. No matter if it’s a tree or a bush or a shrubbery, the entire thing is mostly sugar in various formats but mostly long chain carbohydrates like lignin and cellulose. Plants need three things to make sugar: CO2, H2O and light. In a forest, where tree densities can be quite high, CO2 availability becomes a limiting growth factor. It’d be in the forest interests to have more available CO2 providing for various sugar formation providing the organism with food and structure.
An odd thing about tree leaves, the openings that allow gasses like the ever searched for CO2 are on the bottom of the leaf (these are called stomata). Not many stomata are topside. This suggests that trees and bushes have evolved to find gasses like CO2 from below, not above and this further suggests CO2 might be in higher concentrations nearer the soil.
The soil life (bacterial, fungi etc.) is constantly producing enormous amounts of CO2 and it would stay in the soil forever (eventually killing the very soil life that produces it) if not for tidal forces. Water is everywhere and whether in pools, lakes, oceans or distributed in “moist” soils water moves towards to the moon. The water in the soil and also in the water tables below the soil rise toward the surface every day. When the water rises, it expels the accumulated gasses in the soil into the atmosphere and it’s mostly CO2. It’s a good bet on how leaves developed high populations of stomata on the underside of leaves. As the water relaxes (the tide goes out) it sucks oxygenated air back into the soil to continue the functions of soil life respiration. The soil “breathes” albeit slowly.
The gasses produced by the Forest Walker’s internal combustion engine consist primarily of CO2 and H2O. Combusting sugars produce the same gasses that are needed to construct the sugars because the universe is funny like that. The Forest Walker is constantly laying down these critical construction elements right where the trees need them: close to the ground to be gobbled up by the trees.
The Branch Drones

During the last ice age, giant mammals populated North America - forests and otherwise. Mastodons, woolly mammoths, rhinos, short-faced bears, steppe bison, caribou, musk ox, giant beavers, camels, gigantic ground-dwelling sloths, glyptodons, and dire wolves were everywhere. Many were ten to fifteen feet tall. As they crashed through forests, they would effectively cleave off dead side-branches of trees, halting the spread of a ground-based fire migrating into the tree crown ("laddering") which is a death knell for a forest.
These animals are all extinct now and forests no longer have any manner of pruning services. But, if we build drones fitted with cutting implements like saws and loppers, optical cameras and AI trained to discern dead branches from living ones, these drones could effectively take over pruning services by identifying, cutting, and dropping to the forest floor, dead branches. The dropped branches simply get collected by the Forest Walker as part of its continual mission.
The drones dock on the back of the Forest Walker to recharge their batteries when low. The whole scene would look like a grazing cow with some flies bothering it. This activity breaks the link between a relatively cool ground based fire and the tree crowns and is a vital element in forest fire control.
The Bitcoin Miner

Mining is one of four monetary incentive models, making this system a possibility for development. The other three are US Dept. of the Interior, township, county, and electrical utility company easement contracts for fuel load management, global carbon credits trading, and data set sales. All the above depends on obvious questions getting answered. I will list some obvious ones, but this is not an engineering document and is not the place for spreadsheets. How much Bitcoin one Forest Walker can mine depends on everything else. What amount of biomass can we process? Will that biomass flow enough Syngas to keep the lights on? Can the chassis support enough mining ASICs and supporting infrastructure? What does that weigh and will it affect field performance? How much power can the AC generator produce?
Other questions that are more philosophical persist. Even if a single Forest Walker can only mine scant amounts of BTC per day, that pales to how much fuel material it can process into biochar. We are talking about millions upon millions of forested acres in need of fuel load management. What can a single Forest Walker do? I am not thinking in singular terms. The Forest Walker must operate as a fleet. What could 50 do? 500?
What is it worth providing a service to the world by managing forest fuel loads? Providing proof of work to the global monetary system? Seeding soil with drought and nutrient resilience by the excretion, over time, of carbon by the ton? What did the last forest fire cost?
The Mesh Network

What could be better than one bitcoin mining, carbon sequestering, forest fire squelching, soil amending behemoth? Thousands of them, but then they would need to be able to talk to each other to coordinate position, data handling, etc. Fitted with a mesh networking device, like goTenna or Meshtastic LoRa equipment enables each Forest Walker to communicate with each other.
Now we have an interconnected fleet of Forest Walkers relaying data to each other and more importantly, aggregating all of that to the last link in the chain for uplink. Well, at least Bitcoin mining data. Since block data is lightweight, transmission of these data via mesh networking in fairly close quartered environs is more than doable. So, how does data transmit to the Bitcoin Network? How do the Forest Walkers get the previous block data necessary to execute on mining?
Back To The Chain

Getting Bitcoin block data to and from the network is the last puzzle piece. The standing presumption here is that wherever a Forest Walker fleet is operating, it is NOT within cell tower range. We further presume that the nearest Walmart Wi-Fi is hours away. Enter the Blockstream Satellite or something like it.
A separate, ground-based drone will have two jobs: To stay as close to the nearest Forest Walker as it can and to provide an antennae for either terrestrial or orbital data uplink. Bitcoin-centric data is transmitted to the "uplink drone" via the mesh networked transmitters and then sent on to the uplink and the whole flow goes in the opposite direction as well; many to one and one to many.
We cannot transmit data to the Blockstream satellite, and it will be up to Blockstream and companies like it to provide uplink capabilities in the future and I don't doubt they will. Starlink you say? What’s stopping that company from filtering out block data? Nothing because it’s Starlink’s system and they could decide to censor these data. It seems we may have a problem sending and receiving Bitcoin data in back country environs.
But, then again, the utility of this system in staunching the fuel load that creates forest fires is extremely useful around forested communities and many have fiber, Wi-Fi and cell towers. These communities could be a welcoming ground zero for first deployments of the Forest Walker system by the home and business owners seeking fire repression. In the best way, Bitcoin subsidizes the safety of the communities.
Sensor Packages
LiDaR

The benefit of having a Forest Walker fleet strolling through the forest is the never ending opportunity for data gathering. A plethora of deployable sensors gathering hyper-accurate data on everything from temperature to topography is yet another revenue generator. Data is valuable and the Forest Walker could generate data sales to various government entities and private concerns.
LiDaR (Light Detection and Ranging) can map topography, perform biomass assessment, comparative soil erosion analysis, etc. It so happens that the Forest Walker’s ability to “see,” to navigate about its surroundings, is LiDaR driven and since it’s already being used, we can get double duty by harvesting that data for later use. By using a laser to send out light pulses and measuring the time it takes for the reflection of those pulses to return, very detailed data sets incrementally build up. Eventually, as enough data about a certain area becomes available, the data becomes useful and valuable.
Forestry concerns, both private and public, often use LiDaR to build 3D models of tree stands to assess the amount of harvest-able lumber in entire sections of forest. Consulting companies offering these services charge anywhere from several hundred to several thousand dollars per square kilometer for such services. A Forest Walker generating such assessments on the fly while performing its other functions is a multi-disciplinary approach to revenue generation.
pH, Soil Moisture, and Cation Exchange Sensing

The Forest Walker is quadrupedal, so there are four contact points to the soil. Why not get a pH data point for every step it takes? We can also gather soil moisture data and cation exchange capacities at unheard of densities because of sampling occurring on the fly during commission of the system’s other duties. No one is going to build a machine to do pH testing of vast tracts of forest soils, but that doesn’t make the data collected from such an endeavor valueless. Since the Forest Walker serves many functions at once, a multitude of data products can add to the return on investment component.
Weather Data

Temperature, humidity, pressure, and even data like evapotranspiration gathered at high densities on broad acre scales have untold value and because the sensors are lightweight and don’t require large power budgets, they come along for the ride at little cost. But, just like the old mantra, “gas, grass, or ass, nobody rides for free”, these sensors provide potential revenue benefits just by them being present.
I’ve touched on just a few data genres here. In fact, the question for universities, governmental bodies, and other institutions becomes, “How much will you pay us to attach your sensor payload to the Forest Walker?”
Noise Suppression

Only you can prevent Metallica filling the surrounds with 120 dB of sound. Easy enough, just turn the car stereo off. But what of a fleet of 50 Forest Walkers operating in the backcountry or near a township? 500? 5000? Each one has a wood chipper, an internal combustion engine, hydraulic pumps, actuators, and more cooling fans than you can shake a stick at. It’s a walking, screaming fire-breathing dragon operating continuously, day and night, twenty-four hours a day, three hundred sixty-five days a year. The sound will negatively affect all living things and that impacts behaviors. Serious engineering consideration and prowess must deliver a silencing blow to the major issue of noise.
It would be foolish to think that a fleet of Forest Walkers could be silent, but if not a major design consideration, then the entire idea is dead on arrival. Townships would not allow them to operate even if they solved the problem of widespread fuel load and neither would governmental entities, and rightly so. Nothing, not man nor beast, would want to be subjected to an eternal, infernal scream even if it were to end within days as the fleet moved further away after consuming what it could. Noise and heat are the only real pollutants of this system; taking noise seriously from the beginning is paramount.
Fire Safety

A “fire-breathing dragon” is not the worst description of the Forest Walker. It eats wood, combusts it at very high temperatures and excretes carbon; and it does so in an extremely flammable environment. Bad mix for one Forest Walker, worse for many. One must take extreme pains to ensure that during normal operation, a Forest Walker could fall over, walk through tinder dry brush, or get pounded into the ground by a meteorite from Krypton and it wouldn’t destroy epic swaths of trees and baby deer. I envision an ultimate test of a prototype to include dowsing it in grain alcohol while it’s wrapped up in toilet paper like a pledge at a fraternity party. If it runs for 72 hours and doesn’t set everything on fire, then maybe outside entities won’t be fearful of something that walks around forests with a constant fire in its belly.
The Wrap

How we think about what can be done with and adjacent to Bitcoin is at least as important as Bitcoin’s economic standing itself. For those who will tell me that this entire idea is without merit, I say, “OK, fine. You can come up with something, too.” What can we plug Bitcoin into that, like a battery, makes something that does not work, work? That’s the lesson I get from this entire exercise. No one was ever going to hire teams of humans to go out and "clean the forest". There's no money in that. The data collection and sales from such an endeavor might provide revenues over the break-even point but investment demands Alpha in this day and age. But, plug Bitcoin into an almost viable system and, voilà! We tip the scales to achieve lift-off.
Let’s face it, we haven’t scratched the surface of Bitcoin’s forcing function on our minds. Not because it’s Bitcoin, but because of what that invention means. The question that pushes me to approach things this way is, “what can we create that one system’s waste is another system’s feedstock?” The Forest Walker system’s only real waste is the conversion of low entropy energy (wood and syngas) into high entropy energy (heat and noise). All other output is beneficial to humanity.
Bitcoin, I believe, is the first product of a new mode of human imagination. An imagination newly forged over the past few millennia of being lied to, stolen from, distracted and otherwise mis-allocated to a black hole of the nonsensical. We are waking up.
What I have presented is not science fiction. Everything I have described here is well within the realm of possibility. The question is one of viability, at least in terms of the detritus of the old world we find ourselves departing from. This system would take a non-trivial amount of time and resources to develop. I think the system would garner extensive long-term contracts from those who have the most to lose from wildfires, the most to gain from hyperaccurate data sets, and, of course, securing the most precious asset in the world. Many may not see it that way, for they seek Alpha and are therefore blind to other possibilities. Others will see only the possibilities; of thinking in a new way, of looking at things differently, and dreaming of what comes next.
-
 @ 4ba8e86d:89d32de4
2024-10-07 13:37:38
@ 4ba8e86d:89d32de4
2024-10-07 13:37:38O que é Cwtch? Cwtch (/kʊtʃ/ - uma palavra galesa que pode ser traduzida aproximadamente como “um abraço que cria um lugar seguro”) é um protocolo de mensagens multipartidário descentralizado, que preserva a privacidade, que pode ser usado para construir aplicativos resistentes a metadados.
Como posso pronunciar Cwtch? Como "kutch", para rimar com "butch".
Descentralizado e Aberto : Não existe “serviço Cwtch” ou “rede Cwtch”. Os participantes do Cwtch podem hospedar seus próprios espaços seguros ou emprestar sua infraestrutura para outras pessoas que buscam um espaço seguro. O protocolo Cwtch é aberto e qualquer pessoa é livre para criar bots, serviços e interfaces de usuário e integrar e interagir com o Cwtch.
Preservação de privacidade : toda a comunicação no Cwtch é criptografada de ponta a ponta e ocorre nos serviços cebola Tor v3.
Resistente a metadados : O Cwtch foi projetado de forma que nenhuma informação seja trocada ou disponibilizada a ninguém sem seu consentimento explícito, incluindo mensagens durante a transmissão e metadados de protocolo
Uma breve história do bate-papo resistente a metadados Nos últimos anos, a conscientização pública sobre a necessidade e os benefícios das soluções criptografadas de ponta a ponta aumentou com aplicativos como Signal , Whatsapp e Wire. que agora fornecem aos usuários comunicações seguras.
No entanto, essas ferramentas exigem vários níveis de exposição de metadados para funcionar, e muitos desses metadados podem ser usados para obter detalhes sobre como e por que uma pessoa está usando uma ferramenta para se comunicar.
Uma ferramenta que buscou reduzir metadados é o Ricochet lançado pela primeira vez em 2014. Ricochet usou os serviços cebola Tor v2 para fornecer comunicação criptografada segura de ponta a ponta e para proteger os metadados das comunicações.
Não havia servidores centralizados que auxiliassem no roteamento das conversas do Ricochet. Ninguém além das partes envolvidas em uma conversa poderia saber que tal conversa está ocorrendo.
Ricochet tinha limitações; não havia suporte para vários dispositivos, nem existe um mecanismo para suportar a comunicação em grupo ou para um usuário enviar mensagens enquanto um contato está offline.
Isto tornou a adoção do Ricochet uma proposta difícil; mesmo aqueles em ambientes que seriam melhor atendidos pela resistência aos metadados, sem saber que ela existe.
Além disso, qualquer solução para comunicação descentralizada e resistente a metadados enfrenta problemas fundamentais quando se trata de eficiência, privacidade e segurança de grupo conforme definido pelo consenso e consistência da transcrição.
Alternativas modernas ao Ricochet incluem Briar , Zbay e Ricochet Refresh - cada ferramenta procura otimizar para um conjunto diferente de compensações, por exemplo, Briar procura permitir que as pessoas se comuniquem mesmo quando a infraestrutura de rede subjacente está inoperante, ao mesmo tempo que fornece resistência à vigilância de metadados.
O projeto Cwtch começou em 2017 como um protocolo de extensão para Ricochet, fornecendo conversas em grupo por meio de servidores não confiáveis, com o objetivo de permitir aplicativos descentralizados e resistentes a metadados como listas compartilhadas e quadros de avisos.
Uma versão alfa do Cwtch foi lançada em fevereiro de 2019 e, desde então, a equipe do Cwtch dirigida pela OPEN PRIVACY RESEARCH SOCIETY conduziu pesquisa e desenvolvimento em cwtch e nos protocolos, bibliotecas e espaços de problemas subjacentes.
Modelo de Risco.
Sabe-se que os metadados de comunicações são explorados por vários adversários para minar a segurança dos sistemas, para rastrear vítimas e para realizar análises de redes sociais em grande escala para alimentar a vigilância em massa. As ferramentas resistentes a metadados estão em sua infância e faltam pesquisas sobre a construção e a experiência do usuário de tais ferramentas.
https://nostrcheck.me/media/public/nostrcheck.me_9475702740746681051707662826.webp
O Cwtch foi originalmente concebido como uma extensão do protocolo Ricochet resistente a metadados para suportar comunicações assíncronas de grupos multiponto por meio do uso de infraestrutura anônima, descartável e não confiável.
Desde então, o Cwtch evoluiu para um protocolo próprio. Esta seção descreverá os vários riscos conhecidos que o Cwtch tenta mitigar e será fortemente referenciado no restante do documento ao discutir os vários subcomponentes da Arquitetura Cwtch.
Modelo de ameaça.
É importante identificar e compreender que os metadados são omnipresentes nos protocolos de comunicação; é de facto necessário que tais protocolos funcionem de forma eficiente e em escala. No entanto, as informações que são úteis para facilitar peers e servidores também são altamente relevantes para adversários que desejam explorar tais informações.
Para a definição do nosso problema, assumiremos que o conteúdo de uma comunicação é criptografado de tal forma que um adversário é praticamente incapaz de quebrá-lo veja tapir e cwtch para detalhes sobre a criptografia que usamos, e como tal nos concentraremos em o contexto para os metadados de comunicação.
Procuramos proteger os seguintes contextos de comunicação:
• Quem está envolvido em uma comunicação? Pode ser possível identificar pessoas ou simplesmente identificadores de dispositivos ou redes. Por exemplo, “esta comunicação envolve Alice, uma jornalista, e Bob, um funcionário público”.
• Onde estão os participantes da conversa? Por exemplo, “durante esta comunicação, Alice estava na França e Bob estava no Canadá”.
• Quando ocorreu uma conversa? O momento e a duração da comunicação podem revelar muito sobre a natureza de uma chamada, por exemplo, “Bob, um funcionário público, conversou com Alice ao telefone por uma hora ontem à noite. Esta é a primeira vez que eles se comunicam.” *Como a conversa foi mediada? O fato de uma conversa ter ocorrido por meio de um e-mail criptografado ou não criptografado pode fornecer informações úteis. Por exemplo, “Alice enviou um e-mail criptografado para Bob ontem, enquanto eles normalmente enviam apenas e-mails de texto simples um para o outro”.
• Sobre o que é a conversa? Mesmo que o conteúdo da comunicação seja criptografado, às vezes é possível derivar um contexto provável de uma conversa sem saber exatamente o que é dito, por exemplo, “uma pessoa ligou para uma pizzaria na hora do jantar” ou “alguém ligou para um número conhecido de linha direta de suicídio na hora do jantar”. 3 horas da manhã."
Além das conversas individuais, também procuramos defender-nos contra ataques de correlação de contexto, através dos quais múltiplas conversas são analisadas para obter informações de nível superior:
• Relacionamentos: Descobrir relações sociais entre um par de entidades analisando a frequência e a duração de suas comunicações durante um período de tempo. Por exemplo, Carol e Eve ligam uma para a outra todos os dias durante várias horas seguidas.
• Cliques: Descobrir relações sociais entre um grupo de entidades que interagem entre si. Por exemplo, Alice, Bob e Eva se comunicam entre si.
• Grupos vagamente conectados e indivíduos-ponte: descobrir grupos que se comunicam entre si através de intermediários, analisando cadeias de comunicação (por exemplo, toda vez que Alice fala com Bob, ela fala com Carol quase imediatamente depois; Bob e Carol nunca se comunicam).
• Padrão de Vida: Descobrir quais comunicações são cíclicas e previsíveis. Por exemplo, Alice liga para Eve toda segunda-feira à noite por cerca de uma hora. Ataques Ativos
Ataques de deturpação.
O Cwtch não fornece registro global de nomes de exibição e, como tal, as pessoas que usam o Cwtch são mais vulneráveis a ataques baseados em declarações falsas, ou seja, pessoas que fingem ser outras pessoas:
O fluxo básico de um desses ataques é o seguinte, embora também existam outros fluxos:
•Alice tem um amigo chamado Bob e outro chamado Eve
• Eve descobre que Alice tem um amigo chamado Bob
• Eve cria milhares de novas contas para encontrar uma que tenha uma imagem/chave pública semelhante à de Bob (não será idêntica, mas pode enganar alguém por alguns minutos)
• Eve chama essa nova conta de "Eve New Account" e adiciona Alice como amiga.
• Eve então muda seu nome em "Eve New Account" para "Bob"
• Alice envia mensagens destinadas a "Bob" para a conta falsa de Bob de Eve Como os ataques de declarações falsas são inerentemente uma questão de confiança e verificação, a única maneira absoluta de evitá-los é os usuários validarem absolutamente a chave pública. Obviamente, isso não é o ideal e, em muitos casos, simplesmente não acontecerá .
Como tal, pretendemos fornecer algumas dicas de experiência do usuário na interface do usuário para orientar as pessoas na tomada de decisões sobre confiar em contas e/ou distinguir contas que possam estar tentando se representar como outros usuários.
Uma nota sobre ataques físicos A Cwtch não considera ataques que exijam acesso físico (ou equivalente) à máquina do usuário como praticamente defensáveis. No entanto, no interesse de uma boa engenharia de segurança, ao longo deste documento ainda nos referiremos a ataques ou condições que exigem tal privilégio e indicaremos onde quaisquer mitigações que implementámos falharão.
Um perfil Cwtch.
Os usuários podem criar um ou mais perfis Cwtch. Cada perfil gera um par de chaves ed25519 aleatório compatível com Tor.
Além do material criptográfico, um perfil também contém uma lista de Contatos (outras chaves públicas do perfil Cwtch + dados associados sobre esse perfil, como apelido e (opcionalmente) mensagens históricas), uma lista de Grupos (contendo o material criptográfico do grupo, além de outros dados associados, como apelido do grupo e mensagens históricas).
Conversões entre duas partes: ponto a ponto
https://nostrcheck.me/media/public/nostrcheck.me_2186338207587396891707662879.webp
Para que duas partes participem de uma conversa ponto a ponto, ambas devem estar on-line, mas apenas uma precisa estar acessível por meio do serviço Onion. Por uma questão de clareza, muitas vezes rotulamos uma parte como “ponto de entrada” (aquele que hospeda o serviço cebola) e a outra parte como “ponto de saída” (aquele que se conecta ao serviço cebola).
Após a conexão, ambas as partes adotam um protocolo de autenticação que:
• Afirma que cada parte tem acesso à chave privada associada à sua identidade pública.
• Gera uma chave de sessão efêmera usada para criptografar todas as comunicações futuras durante a sessão.
Esta troca (documentada com mais detalhes no protocolo de autenticação ) é negável offline , ou seja, é possível para qualquer parte falsificar transcrições desta troca de protocolo após o fato e, como tal - após o fato - é impossível provar definitivamente que a troca aconteceu de forma alguma.
Após o protocolo de autenticação, as duas partes podem trocar mensagens livremente.
Conversas em Grupo e Comunicação Ponto a Servidor
Ao iniciar uma conversa em grupo, é gerada uma chave aleatória para o grupo, conhecida como Group Key. Todas as comunicações do grupo são criptografadas usando esta chave. Além disso, o criador do grupo escolhe um servidor Cwtch para hospedar o grupo. Um convite é gerado, incluindo o Group Key, o servidor do grupo e a chave do grupo, para ser enviado aos potenciais membros.
Para enviar uma mensagem ao grupo, um perfil se conecta ao servidor do grupo e criptografa a mensagem usando a Group Key, gerando também uma assinatura sobre o Group ID, o servidor do grupo e a mensagem. Para receber mensagens do grupo, um perfil se conecta ao servidor e baixa as mensagens, tentando descriptografá-las usando a Group Key e verificando a assinatura.
Detalhamento do Ecossistema de Componentes
O Cwtch é composto por várias bibliotecas de componentes menores, cada uma desempenhando um papel específico. Algumas dessas bibliotecas incluem:
- abertoprivacidade/conectividade: Abstração de rede ACN, atualmente suportando apenas Tor.
- cwtch.im/tapir: Biblioteca para construção de aplicativos p2p em sistemas de comunicação anônimos.
- cwtch.im/cwtch: Biblioteca principal para implementação do protocolo/sistema Cwtch.
- cwtch.im/libcwtch-go: Fornece ligações C para Cwtch para uso em implementações de UI.
TAPIR: Uma Visão Detalhada
Projetado para substituir os antigos canais de ricochete baseados em protobuf, o Tapir fornece uma estrutura para a construção de aplicativos anônimos.
Está dividido em várias camadas:
• Identidade - Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um par.
• Conexões – O protocolo de rede bruto que conecta dois pares. Até agora, as conexões são definidas apenas através do Tor v3 Onion Services.
• Aplicativos - As diversas lógicas que permitem um determinado fluxo de informações em uma conexão. Os exemplos incluem transcrições criptográficas compartilhadas, autenticação, proteção contra spam e serviços baseados em tokens. Os aplicativos fornecem recursos que podem ser referenciados por outros aplicativos para determinar se um determinado peer tem a capacidade de usar um determinado aplicativo hospedado.
• Pilhas de aplicativos - Um mecanismo para conectar mais de um aplicativo, por exemplo, a autenticação depende de uma transcrição criptográfica compartilhada e o aplicativo peer cwtch principal é baseado no aplicativo de autenticação.
Identidade.
Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um peer.
InitializeIdentity - de um par de chaves conhecido e persistente:i,I
InitializeEphemeralIdentity - de um par de chaves aleatório: ie,Ie
Aplicativos de transcrição.
Inicializa uma transcrição criptográfica baseada em Merlin que pode ser usada como base de protocolos baseados em compromisso de nível superior
O aplicativo de transcrição entrará em pânico se um aplicativo tentar substituir uma transcrição existente por uma nova (aplicando a regra de que uma sessão é baseada em uma e apenas uma transcrição).
Merlin é uma construção de transcrição baseada em STROBE para provas de conhecimento zero. Ele automatiza a transformação Fiat-Shamir, para que, usando Merlin, protocolos não interativos possam ser implementados como se fossem interativos.
Isto é significativamente mais fácil e menos sujeito a erros do que realizar a transformação manualmente e, além disso, também fornece suporte natural para:
• protocolos multi-round com fases alternadas de commit e desafio;
• separação natural de domínios, garantindo que os desafios estejam vinculados às afirmações a serem provadas;
• enquadramento automático de mensagens, evitando codificação ambígua de dados de compromisso;
• e composição do protocolo, usando uma transcrição comum para vários protocolos.
Finalmente, o Merlin também fornece um gerador de números aleatórios baseado em transcrição como defesa profunda contra ataques de entropia ruim (como reutilização de nonce ou preconceito em muitas provas). Este RNG fornece aleatoriedade sintética derivada de toda a transcrição pública, bem como dos dados da testemunha do provador e uma entrada auxiliar de um RNG externo.
Conectividade Cwtch faz uso do Tor Onion Services (v3) para todas as comunicações entre nós.
Fornecemos o pacote openprivacy/connectivity para gerenciar o daemon Tor e configurar e desmontar serviços cebola através do Tor.
Criptografia e armazenamento de perfil.
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir uma senha.
Perfis não criptografados e a senha padrão Para lidar com perfis "não criptografados" (ou seja, que não exigem senha para serem abertos), atualmente criamos um perfil com uma senha codificada de fato .
Isso não é o ideal, preferiríamos confiar no material de chave fornecido pelo sistema operacional, de modo que o perfil fosse vinculado a um dispositivo específico, mas esses recursos são atualmente uma colcha de retalhos - também notamos, ao criar um perfil não criptografado, pessoas que usam Cwtch estão explicitamente optando pelo risco de que alguém com acesso ao sistema de arquivos possa descriptografar seu perfil.
Vulnerabilidades Relacionadas a Imagens e Entrada de Dados
Imagens Maliciosas
O Cwtch enfrenta desafios na renderização de imagens, com o Flutter utilizando Skia, embora o código subjacente não seja totalmente seguro para a memória.
Realizamos testes de fuzzing nos componentes Cwtch e encontramos um bug de travamento causado por um arquivo GIF malformado, levando a falhas no kernel. Para mitigar isso, adotamos a política de sempre habilitar cacheWidth e/ou cacheHeight máximo para widgets de imagem.
Identificamos o risco de imagens maliciosas serem renderizadas de forma diferente em diferentes plataformas, como evidenciado por um bug no analisador PNG da Apple.
Riscos de Entrada de Dados
Um risco significativo é a interceptação de conteúdo ou metadados por meio de um Input Method Editor (IME) em dispositivos móveis. Mesmo aplicativos IME padrão podem expor dados por meio de sincronização na nuvem, tradução online ou dicionários pessoais.
Implementamos medidas de mitigação, como enableIMEPersonalizedLearning: false no Cwtch 1.2, mas a solução completa requer ações em nível de sistema operacional e é um desafio contínuo para a segurança móvel.
Servidor Cwtch.
O objetivo do protocolo Cwtch é permitir a comunicação em grupo através de infraestrutura não confiável .
Ao contrário dos esquemas baseados em retransmissão, onde os grupos atribuem um líder, um conjunto de líderes ou um servidor confiável de terceiros para garantir que cada membro do grupo possa enviar e receber mensagens em tempo hábil (mesmo que os membros estejam offline) - infraestrutura não confiável tem o objetivo de realizar essas propriedades sem a suposição de confiança.
O artigo original do Cwtch definia um conjunto de propriedades que se esperava que os servidores Cwtch fornecessem:
• O Cwtch Server pode ser usado por vários grupos ou apenas um.
• Um servidor Cwtch, sem a colaboração de um membro do grupo, nunca deve aprender a identidade dos participantes de um grupo.
• Um servidor Cwtch nunca deve aprender o conteúdo de qualquer comunicação.
• Um servidor Cwtch nunca deve ser capaz de distinguir mensagens como pertencentes a um grupo específico. Observamos aqui que essas propriedades são um superconjunto dos objetivos de design das estruturas de Recuperação de Informações Privadas.
Melhorias na Eficiência e Segurança
Eficiência do Protocolo
Atualmente, apenas um protocolo conhecido, o PIR ingênuo, atende às propriedades desejadas para garantir a privacidade na comunicação do grupo Cwtch. Este método tem um impacto direto na eficiência da largura de banda, especialmente para usuários em dispositivos móveis. Em resposta a isso, estamos ativamente desenvolvendo novos protocolos que permitem negociar garantias de privacidade e eficiência de maneiras diversas.
Os servidores, no momento desta escrita, permitem o download completo de todas as mensagens armazenadas, bem como uma solicitação para baixar mensagens específicas a partir de uma determinada mensagem. Quando os pares ingressam em um grupo em um novo servidor, eles baixam todas as mensagens do servidor inicialmente e, posteriormente, apenas as mensagens novas.
Mitigação de Análise de Metadados
Essa abordagem permite uma análise moderada de metadados, pois o servidor pode enviar novas mensagens para cada perfil suspeito exclusivo e usar essas assinaturas de mensagens exclusivas para rastrear sessões ao longo do tempo. Essa preocupação é mitigada por dois fatores:
- Os perfis podem atualizar suas conexões a qualquer momento, resultando em uma nova sessão do servidor.
- Os perfis podem ser "ressincronizados" de um servidor a qualquer momento, resultando em uma nova chamada para baixar todas as mensagens. Isso é comumente usado para buscar mensagens antigas de um grupo.
Embora essas medidas imponham limites ao que o servidor pode inferir, ainda não podemos garantir resistência total aos metadados. Para soluções futuras para esse problema, consulte Niwl.
Proteção contra Pares Maliciosos
Os servidores enfrentam o risco de spam gerado por pares, representando uma ameaça significativa à eficácia do sistema Cwtch. Embora tenhamos implementado um mecanismo de proteção contra spam no protótipo do Cwtch, exigindo que os pares realizem alguma prova de trabalho especificada pelo servidor, reconhecemos que essa não é uma solução robusta na presença de um adversário determinado com recursos significativos.
Pacotes de Chaves
Os servidores Cwtch se identificam por meio de pacotes de chaves assinados, contendo uma lista de chaves necessárias para garantir a segurança e resistência aos metadados na comunicação do grupo Cwtch. Esses pacotes de chaves geralmente incluem três chaves: uma chave pública do serviço Tor v3 Onion para o Token Board, uma chave pública do Tor v3 Onion Service para o Token Service e uma chave pública do Privacy Pass.
Para verificar os pacotes de chaves, os perfis que os importam do servidor utilizam o algoritmo trust-on-first-use (TOFU), verificando a assinatura anexada e a existência de todos os tipos de chave. Se o perfil já tiver importado o pacote de chaves do servidor anteriormente, todas as chaves são consideradas iguais.
Configuração prévia do aplicativo para ativar o Relé do Cwtch.
No Android, a hospedagem de servidor não está habilitada, pois essa opção não está disponível devido às limitações dos dispositivos Android. Essa funcionalidade está reservada apenas para servidores hospedados em desktops.
No Android, a única forma direta de importar uma chave de servidor é através do grupo de teste Cwtch, garantindo assim acesso ao servidor Cwtch.
Primeiro passo é Habilitar a opção de grupo no Cwtch que está em fase de testes. Clique na opção no canto superior direito da tela de configuração e pressione o botão para acessar as configurações do Cwtch.
Você pode alterar o idioma para Português do Brasil.Depois, role para baixo e selecione a opção para ativar os experimentos. Em seguida, ative a opção para habilitar o chat em grupo e a pré-visualização de imagens e fotos de perfil, permitindo que você troque sua foto de perfil.
https://link.storjshare.io/raw/jvss6zxle26jdguwaegtjdixhfka/production/f0ca039733d48895001261ab25c5d2efbaf3bf26e55aad3cce406646f9af9d15.MP4
Próximo passo é Criar um perfil.
Pressione o + botão de ação no canto inferior direito e selecione "Novo perfil" ou aberta no botão + adicionar novo perfil.
-
Selecione um nome de exibição
-
Selecione se deseja proteger
este perfil e salvo localmente com criptografia forte: Senha: sua conta está protegida de outras pessoas que possam usar este dispositivo
Sem senha: qualquer pessoa que tenha acesso a este dispositivo poderá acessar este perfil.
Preencha sua senha e digite-a novamente
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a chave da senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir um senha.
https://link.storjshare.io/raw/jxqbqmur2lcqe2eym5thgz4so2ya/production/8f9df1372ec7e659180609afa48be22b12109ae5e1eda9ef1dc05c1325652507.MP4
O próximo passo é adicionar o FuzzBot, que é um bot de testes e de desenvolvimento.
Contato do FuzzBot: 4y2hxlxqzautabituedksnh2ulcgm2coqbure6wvfpg4gi2ci25ta5ad.
Ao enviar o comando "testgroup-invite" para o FuzzBot, você receberá um convite para entrar no Grupo Cwtch Test. Ao ingressar no grupo, você será automaticamente conectado ao servidor Cwtch. Você pode optar por sair do grupo a qualquer momento ou ficar para conversar e tirar dúvidas sobre o aplicativo e outros assuntos. Depois, você pode configurar seu próprio servidor Cwtch, o que é altamente recomendável.
https://link.storjshare.io/raw/jvji25zclkoqcouni5decle7if7a/production/ee3de3540a3e3dca6e6e26d303e12c2ef892a5d7769029275b8b95ffc7468780.MP4
Agora você pode utilizar o aplicativo normalmente. Algumas observações que notei: se houver demora na conexão com outra pessoa, ambas devem estar online. Se ainda assim a conexão não for estabelecida, basta clicar no ícone de reset do Tor para restabelecer a conexão com a outra pessoa.
Uma introdução aos perfis Cwtch.
Com Cwtch você pode criar um ou mais perfis . Cada perfil gera um par de chaves ed25519 aleatório compatível com a Rede Tor.
Este é o identificador que você pode fornecer às pessoas e que elas podem usar para entrar em contato com você via Cwtch.
Cwtch permite criar e gerenciar vários perfis separados. Cada perfil está associado a um par de chaves diferente que inicia um serviço cebola diferente.
Gerenciar Na inicialização, o Cwtch abrirá a tela Gerenciar Perfis. Nessa tela você pode:
- Crie um novo perfil.
- Desbloquear perfis.
- Criptografados existentes.
- Gerenciar perfis carregados.
- Alterando o nome de exibição de um perfil.
- Alterando a senha de um perfil Excluindo um perfil.
- Alterando uma imagem de perfil.
Backup ou exportação de um perfil.
Na tela de gerenciamento de perfil:
-
Selecione o lápis ao lado do perfil que você deseja editar
-
Role para baixo até a parte inferior da tela.
-
Selecione "Exportar perfil"
-
Escolha um local e um nome de arquivo.
5.confirme.
Uma vez confirmado, o Cwtch colocará uma cópia do perfil no local indicado. Este arquivo é criptografado no mesmo nível do perfil.
Este arquivo pode ser importado para outra instância do Cwtch em qualquer dispositivo.
Importando um perfil.
-
Pressione o +botão de ação no canto inferior direito e selecione "Importar perfil"
-
Selecione um arquivo de perfil Cwtch exportado para importar
-
Digite a senha associada ao perfil e confirme.
Uma vez confirmado, o Cwtch tentará descriptografar o arquivo fornecido usando uma chave derivada da senha fornecida. Se for bem-sucedido, o perfil aparecerá na tela Gerenciamento de perfil e estará pronto para uso.
OBSERVAÇÃO Embora um perfil possa ser importado para vários dispositivos, atualmente apenas uma versão de um perfil pode ser usada em todos os dispositivos ao mesmo tempo. As tentativas de usar o mesmo perfil em vários dispositivos podem resultar em problemas de disponibilidade e falhas de mensagens.
Qual é a diferença entre uma conexão ponto a ponto e um grupo cwtch?
As conexões ponto a ponto Cwtch permitem que 2 pessoas troquem mensagens diretamente. As conexões ponto a ponto nos bastidores usam serviços cebola Tor v3 para fornecer uma conexão criptografada e resistente a metadados. Devido a esta conexão direta, ambas as partes precisam estar online ao mesmo tempo para trocar mensagens.
Os Grupos Cwtch permitem que várias partes participem de uma única conversa usando um servidor não confiável (que pode ser fornecido por terceiros ou auto-hospedado). Os operadores de servidores não conseguem saber quantas pessoas estão em um grupo ou o que está sendo discutido. Se vários grupos estiverem hospedados em um único servidor, o servidor não conseguirá saber quais mensagens pertencem a qual grupo sem a conivência de um membro do grupo. Ao contrário das conversas entre pares, as conversas em grupo podem ser conduzidas de forma assíncrona, para que todos num grupo não precisem estar online ao mesmo tempo.
Por que os grupos cwtch são experimentais? Mensagens em grupo resistentes a metadados ainda são um problema em aberto . Embora a versão que fornecemos no Cwtch Beta seja projetada para ser segura e com metadados privados, ela é bastante ineficiente e pode ser mal utilizada. Como tal, aconselhamos cautela ao usá-lo e apenas o fornecemos como um recurso opcional.
Como posso executar meu próprio servidor Cwtch? A implementação de referência para um servidor Cwtch é de código aberto . Qualquer pessoa pode executar um servidor Cwtch, e qualquer pessoa com uma cópia do pacote de chaves públicas do servidor pode hospedar grupos nesse servidor sem que o operador tenha acesso aos metadados relacionados ao grupo .
https://git.openprivacy.ca/cwtch.im/server
https://docs.openprivacy.ca/cwtch-security-handbook/server.html
Como posso desligar o Cwtch? O painel frontal do aplicativo possui um ícone do botão "Shutdown Cwtch" (com um 'X'). Pressionar este botão irá acionar uma caixa de diálogo e, na confirmação, o Cwtch será desligado e todos os perfis serão descarregados.
Suas doações podem fazer a diferença no projeto Cwtch? O Cwtch é um projeto dedicado a construir aplicativos que preservam a privacidade, oferecendo comunicação de grupo resistente a metadados. Além disso, o projeto também desenvolve o Cofre, formulários da web criptografados para ajudar mútua segura. Suas contribuições apoiam iniciativas importantes, como a divulgação de violações de dados médicos em Vancouver e pesquisas sobre a segurança do voto eletrônico na Suíça. Ao doar, você está ajudando a fechar o ciclo, trabalhando com comunidades marginalizadas para identificar e corrigir lacunas de privacidade. Além disso, o projeto trabalha em soluções inovadoras, como a quebra de segredos através da criptografia de limite para proteger sua privacidade durante passagens de fronteira. E também tem a infraestrutura: toda nossa infraestrutura é open source e sem fins lucrativos. Conheça também o Fuzzytags, uma estrutura criptográfica probabilística para marcação resistente a metadados. Sua doação é crucial para continuar o trabalho em prol da privacidade e segurança online. Contribua agora com sua doação
https://openprivacy.ca/donate/
onde você pode fazer sua doação em bitcoin e outras moedas, e saiba mais sobre os projetos. https://openprivacy.ca/work/
Link sobre Cwtch
https://cwtch.im/
https://git.openprivacy.ca/cwtch.im/cwtch
https://docs.cwtch.im/docs/intro
https://docs.openprivacy.ca/cwtch-security-handbook/
Baixar #CwtchDev
cwtch.im/download/
https://play.google.com/store/apps/details?id=im.cwtch.flwtch
-
 @ fd78c37f:a0ec0833
2025-01-17 03:23:02
@ fd78c37f:a0ec0833
2025-01-17 03:23:02In this edition, we invited Evelyn and Gerardo to share their experiences in creating a Bitcoin community, discussing their motivations, challenges, strategies, and goals. Their journey offers valuable lessons on community engagement and the transformative power of Bitcoin.
YakiHonne: Evelyn, Gerardo, We're truly delighted and grateful to have you join us today. Before we dive in, I’d like to share some background on what YakiHonne is. YakiHonne is a decentralized media client built on the Nostr protocol that enables freedom of speech through technology. It empowers creators to create their own voice, assets, and features. It also allows features like smart widgets, verified notes, and focuses on long-form articles. we'll be exploring more about your community. What sparked your interest in Bitcoin, and what motivated you to create a community around it ?
Evelyn:In the beginning, I started learning about Bitcoin in 2019, just a bit at first. When it became legal tender, we realized it was a monumental moment for El Salvador, and we knew we had to get involved in anything related to Bitcoin. Personally, I began watching videos and reading more about Bitcoin to deepen my understanding of its significance for El Salvador adopting it as legal tender. Evelyn:Soon, I recognized the importance of educating more Salvadorans about Bitcoin. This led us to start providing Bitcoin education in classrooms, schools, and various communities across different cities in El Salvador. As we traveled across the country, we noticed that Bitcoin adoption was still limited, with few places accepting it as a means of payment. This observation motivated us to build a community where Bitcoin could be used as a medium of exchange. Our goal was to replicate and expand upon the Bitcoin community that was already taking root in El Salvador.As the first country to adopt Bitcoin as legal tender, we understood the necessity of working on increasing its adoption throughout the nation.

YakiHonne: Could you share how your community was established, the strategies you employed to attract members, and the challenges you faced in the process?
Gerardo:We were living in San Salvador, but we didn’t enjoy city life, so we started looking for a place outside the city. We knew we wanted to live in the mountains, and there are a few options here in El Salvador. Eventually, we found ourselves in Berlin, and we really liked it. After spending some time visiting and getting to know the people, we decided this was where we wanted to settle down.
 Gerardo:Once we made that decision, we knew we wanted to start teaching Bitcoin within the community. We began talking to local entrepreneurs and residents, letting them know about our plan to educate the community about Bitcoin. We explained that it could bring significant opportunities for Berlin and its residents, including increased tourism. Some people were really excited about the idea because there weren’t many places in El Salvador, the “Bitcoin country” that had a circular economy focused on Bitcoin. Most of the activity was concentrated in the city.
Gerardo:As people started to hear about our idea, they liked it, and soon we had a team working with us to onboard more businesses. We were fortunate to find the right people, and that’s how it all began. We started by getting about 12 to 15 businesses to accept Bitcoin. I remember creating a social media presence, including a Twitter account, to promote Berlin as a destination where people could spend Bitcoin.
Gerardo:Berlin is about two and a half to three hours from the capital, San Salvador, depending on traffic, so it wasn’t easy for people to come initially. But as time went on, more people started visiting. They liked the weather, the friendly community, and the places where they could use Bitcoin. Soon, a few Bitcoin enthusiasts even moved to Berlin.
Gerardo:A year and eight months later, we now have a thriving community of over 20 Bitcoin users from around the world living here, along with many locals who have become Bitcoin users thanks to our educational efforts. We’ve established a Bitcoin center, have over 130 merchants accepting Bitcoin, and even non-business residents are using it. It’s been a fantastic journey, and it all started with a desire to educate a few people, which kept growing from there.
Gerardo:Once we made that decision, we knew we wanted to start teaching Bitcoin within the community. We began talking to local entrepreneurs and residents, letting them know about our plan to educate the community about Bitcoin. We explained that it could bring significant opportunities for Berlin and its residents, including increased tourism. Some people were really excited about the idea because there weren’t many places in El Salvador, the “Bitcoin country” that had a circular economy focused on Bitcoin. Most of the activity was concentrated in the city.
Gerardo:As people started to hear about our idea, they liked it, and soon we had a team working with us to onboard more businesses. We were fortunate to find the right people, and that’s how it all began. We started by getting about 12 to 15 businesses to accept Bitcoin. I remember creating a social media presence, including a Twitter account, to promote Berlin as a destination where people could spend Bitcoin.
Gerardo:Berlin is about two and a half to three hours from the capital, San Salvador, depending on traffic, so it wasn’t easy for people to come initially. But as time went on, more people started visiting. They liked the weather, the friendly community, and the places where they could use Bitcoin. Soon, a few Bitcoin enthusiasts even moved to Berlin.
Gerardo:A year and eight months later, we now have a thriving community of over 20 Bitcoin users from around the world living here, along with many locals who have become Bitcoin users thanks to our educational efforts. We’ve established a Bitcoin center, have over 130 merchants accepting Bitcoin, and even non-business residents are using it. It’s been a fantastic journey, and it all started with a desire to educate a few people, which kept growing from there.

YakiHonne: I love how it all started and the fact that you created mechanisms and opportunities for Bitcoiners to actually spend Bitcoin. It's also amazing how this initiative helped Berlin by attracting more prominent investors to settle here.Apart from Berlin's distance from the capital, which made it less accessible and may have deterred some people from coming, were there any other challenges you faced in the process of promoting Bitcoin adoption?
Gerardo:we faced several challenges, such as the local government’s disapproval of our Bitcoin activities, the initial difficulty of introducing Bitcoin into the community, and finding a suitable venue for our educational efforts. These were the primary obstacles we encountered early in the project. Gerardo:The first challenge we faced in the beginning was the lack of Bitcoin usage in the town. While we were teaching people to accept Bitcoin, there weren’t many individuals actually spending it. It was just the two of us at first, taking turns visiting places that accept Bitcoin, trying to make sure we could spend it and show others that it was possible. We were also traveling to San Salvador and inviting people to come to Berlin, but our efforts weren’t very successful initially. Gerardo:Eventually, more people started coming, and that issue was resolved. However, another challenge arose with some local politicians who didn’t approve of what we were doing. They tried to stop our efforts by discouraging people from working with us. As a result, a few locals didn’t trust us at first. Gerardo:For some people, they might think it's a scam. So, the educational aspect was a significant challenge. A few months into the project, we decided to hold community meetings, which was crucial for us because we needed a place to teach and spread knowledge about Bitcoin. However, we didn't have a dedicated venue at the time. Fortunately, we had a few friends, and initially, we held meetings at their homes or garages.

YakiHonne: You mentioned facing trust issues. What principles guide the community, and how did you maintain trust and reliability in your discussions as you built the community?
Evelyn:One of the key points in building trust within the local community is establishing clear trust and transparency. There were many misconceptions about Bitcoin initially. People often associated Bitcoin with politics and politicians, assuming it was a government creation. This misconception was fueled by the distribution of a government-issued Bitcoin wallet tied to citizens’ IDs, which caused confusion due to a lack of public education on Bitcoin. Evelyn:To address this, we made it a priority to remain neutral and uninvolved with the government. We focused on educating people about Bitcoin's origins, its creation by Satoshi Nakamoto, and its fundamental workings, breaking down complex concepts into simple explanations. We also informed the community about various Bitcoin wallets available, emphasizing alternatives to the government-issued wallet, which had issues with trust and identity theft. Evelyn:Engaging with respected elders in Berlin was another crucial strategy. We explained the benefits of Bitcoin adoption for the local economy and how it could improve the quality of life in the community. These respected community members helped us reach others and build credibility. Evelyn:Since May 2023, we have been deeply involved in educational and social projects, demonstrating that Bitcoin can improve not only personal financial situations but also community welfare. Importantly, we never asked for anything in return, showing our genuine intentions. Over time, this consistent engagement helped us gain the community’s trust, and our work in Bitcoin education has grown stronger.

YakiHonne: How do you educate your members and keep them informed about the latest Bitcoin developments?
Evelyn:Beyond simply observing developments in the Bitcoin space, we hold weekly meetings not only within our team but also with the broader community. These gatherings have been invaluable, as we've been fortunate to engage with many knowledgeable individuals who bring both technical expertise and insights into the philosophical aspects of Bitcoin. Through these interactions, we continuously learn from each other. We've also had the privilege of hosting experts who conduct workshops and deliver lectures during our meetings. These sessions help us stay informed about the latest advancements in technology and the evolving landscape of Bitcoin.

YakiHonne: Apart from education and inviting external instructors for weekly classes and meetups, how does your community collaborate with the broader Bitcoin ecosystem? What partnership has been the most impactful so far?
Gerardo:When we arrived here, I remember that many people knew something needed to change in the town’s technology and overall situation. They were unhappy with the status quo, especially with the government. There was already a lot of energy within the population of Berlin; we just needed to harness that energy and get organized. That’s when people started collaborating. Gerardo:In addition to Bitcoin education, we worked on social projects, like painting parks, cleaning the city, and addressing basic issues that the municipality wasn’t tackling. This shift in mentality helped people realize that it’s up to us to take action, not just wait for the government to act. Gerardo:As for Bitcoin adoption, many businesses have greatly benefited from it. They’ve seen an increase in income and are now able to save in new ways. You can even hear personal stories from business owners on how their operations have gradually transformed since they started accepting Bitcoin. This has had a significant impact on the local economy and also on how people view social change within the town.
YakiHonne: Do you have any partnerships with other Bitcoin or Bitcoin-related communities outside of Berlin?
Gerardo:There aren’t many Bitcoin communities outside of Berlin, even though we're considered the Bitcoin country. There's the Los Angeles one, which was the first, then Bitcoin Beach, followed by us, and now a new one is emerging in Santa Ana. I had a conversation yesterday with someone who's helping with that initiative, and we're planning some collaborations with them. They’ll be visiting us here, and we’ll also visit them to collaborate on Bitcoin education. There's also another community in La Pi Raya, a small island, that is working on Bitcoin education as well. Gerardo: There aren't many communities in the area, but we’re always open to working with them. It's really interesting to hear about their experiences and the challenges they face, as we can learn a lot from their insights.
YakiHonne: I expected that, since it was El Salvador, there would be over a thousand Bitcoin communities. Given that it's a country that has embraced Bitcoin so extensively, I thought there would be hundreds of communities.
Gerardo:However, it's been three and a half years since the Bitcoin Law, and adoption has been slow. While the U.S. dollar is still the other currency in use, people continue to trust it despite its devaluation. It's relatively stable, so they don’t yet feel the need to switch to Bitcoin. So, the adoption process is definitely moving slowly.
YakiHonne: Apart from creating Bitcoin-friendly shops and a community where people can buy and trade with BTC, what other steps have been taken to promote Bitcoin adoption in El Salvador? What results have you seen so far in your community?.
Gerardo:Bringing Bitcoin's identity to Berlin has significantly helped the town. It has attracted more Bitcoiners, especially those coming from El Salvador who are interested in Bitcoin adoption. We've started claiming the title of "Bitcoin City of El Salvador," which has also helped. The results are clear: people are seeing their income improve and are learning new things from the Bitcoin community. Slowly but surely, Berlin is adopting Bitcoin, and it’s bringing positive changes to the town.

YakiHonne: What are the community's goals for the next 6-12 months, and how do you see it evolving with Bitcoin's growth?
Gerardo:While many Berliners use Bitcoin for transactions, they tend to store it in custodial wallets. Our goal is to encourage people to own their seed phrases and understand the full Bitcoin philosophy, including the importance of time preference. We aim to teach people not just about Bitcoin payments, but also its broader value this year. Gerardo:we’ll create an independent association to manage donations and oversee community projects. The association will have its own rules, a board consisting of both expats and locals, and will work on improving the town. The Bitcoin education aspect will remain under our care. Our main goals are better education and local involvement in fixing the town's issues.
YakiHonne: You mentioned saving Bitcoin, and it reminded me of a point made in a previous interview with another community. They said the same thing—many people spend Bitcoin, but few actually save it, which is a problem. Saving Bitcoin has many benefits. For example, that community even encourages parents to save Bitcoin for their children, so that by the time they grow up, they'll have something valuable to inherit. I really appreciate your insights today, and I look forward to seeing how these efforts continue to make an impact in the future.
-
 @ a95c6243:d345522c
2024-11-29 19:45:43
@ a95c6243:d345522c
2024-11-29 19:45:43Konsum ist Therapie.
Wolfgang JoopUmweltbewusstes Verhalten und verantwortungsvoller Konsum zeugen durchaus von einer wünschenswerten Einstellung. Ob man deswegen allerdings einen grünen statt eines schwarzen Freitags braucht, darf getrost bezweifelt werden – zumal es sich um manipulatorische Konzepte handelt. Wie in der politischen Landschaft sind auch hier die Etiketten irgendwas zwischen nichtssagend und trügerisch.
Heute ist also wieder mal «Black Friday», falls Sie es noch nicht mitbekommen haben sollten. Eigentlich haben wir ja eher schon eine ganze «Black Week», der dann oft auch noch ein «Cyber Monday» folgt. Die Werbebranche wird nicht müde, immer neue Anlässe zu erfinden oder zu importieren, um uns zum Konsumieren zu bewegen. Und sie ist damit sehr erfolgreich.
Warum fallen wir auf derartige Werbetricks herein und kaufen im Zweifelsfall Dinge oder Mengen, die wir sicher nicht brauchen? Pure Psychologie, würde ich sagen. Rabattschilder triggern etwas in uns, was den Verstand in Stand-by versetzt. Zusätzlich beeinflussen uns alle möglichen emotionalen Reize und animieren uns zum Schnäppchenkauf.
Gedankenlosigkeit und Maßlosigkeit können besonders bei der Ernährung zu ernsten Problemen führen. Erst kürzlich hat mir ein Bekannter nach einer USA-Reise erzählt, dass es dort offenbar nicht unüblich ist, schon zum ausgiebigen Frühstück in einem Restaurant wenigstens einen Liter Cola zu trinken. Gerne auch mehr, um das Gratis-Nachfüllen des Bechers auszunutzen.
Kritik am schwarzen Freitag und dem unnötigen Konsum kommt oft von Umweltschützern. Neben Ressourcenverschwendung, hohem Energieverbrauch und wachsenden Müllbergen durch eine zunehmende Wegwerfmentalität kommt dabei in der Regel auch die «Klimakrise» auf den Tisch.
Die EU-Kommission lancierte 2015 den Begriff «Green Friday» im Kontext der überarbeiteten Rechtsvorschriften zur Kennzeichnung der Energieeffizienz von Elektrogeräten. Sie nutzte die Gelegenheit kurz vor dem damaligen schwarzen Freitag und vor der UN-Klimakonferenz COP21, bei der das Pariser Abkommen unterzeichnet werden sollte.
Heute wird ein grüner Freitag oft im Zusammenhang mit der Forderung nach «nachhaltigem Konsum» benutzt. Derweil ist die Europäische Union schon weit in ihr Geschäftsmodell des «Green New Deal» verstrickt. In ihrer Propaganda zum Klimawandel verspricht sie tatsächlich «Unterstützung der Menschen und Regionen, die von immer häufigeren Extremwetter-Ereignissen betroffen sind». Was wohl die Menschen in der Region um Valencia dazu sagen?
Ganz im Sinne des Great Reset propagierten die Vereinten Nationen seit Ende 2020 eine «grüne Erholung von Covid-19, um den Klimawandel zu verlangsamen». Der UN-Umweltbericht sah in dem Jahr einen Schwerpunkt auf dem Verbraucherverhalten. Änderungen des Konsumverhaltens des Einzelnen könnten dazu beitragen, den Klimaschutz zu stärken, hieß es dort.
Der Begriff «Schwarzer Freitag» wurde in den USA nicht erstmals für Einkäufe nach Thanksgiving verwendet – wie oft angenommen –, sondern für eine Finanzkrise. Jedoch nicht für den Börsencrash von 1929, sondern bereits für den Zusammenbruch des US-Goldmarktes im September 1869. Seitdem mussten die Menschen weltweit so einige schwarze Tage erleben.
Kürzlich sind die britischen Aufsichtsbehörden weiter von ihrer Zurückhaltung nach dem letzten großen Finanzcrash von 2008 abgerückt. Sie haben Regeln für den Bankensektor gelockert, womit sie «verantwortungsvolle Risikobereitschaft» unterstützen wollen. Man würde sicher zu schwarz sehen, wenn man hier ein grünes Wunder befürchten würde.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ a42048d7:26886c32
2025-01-04 22:32:52
@ a42048d7:26886c32
2025-01-04 22:32:52OP_CAT, Coffee, and keeping an open mind to Bitcoin soft forks by an 80 IQ BTC Maxi Pleb
TLDR: CAT is both low risk and low appeal to the broader non-dev BTC community. I don’t care and you shouldn’t either. If I am an 80 IQ HODL pleb or a company that caters to that group, can you please give me 2-4 fifth grade level coherent english sentences that explain why I should support CAT? I’m still waiting… CTV or LNHANCE on the other hand have broad appeal.
Five years ago in the office we got a fancy $6,000 coffee maker. It was hooked up to wifi, showed TV on a giant screen, and could make every type of coffee/milkshake you could think of. I was captivated… for about 1 day. After trying a few times I realized almost all the drinks it made were of low quality. The wifi connection actually ended up just being annoying. Half the time I wanted a coffee, only had a 5 minute break, and the machine displayed some inscrutable error. I went back to the proverbial grind un-caffeinated and frustrated wishing we had the old reliable boring coffee maker back. I also found myself only coming back to the 2 drinks I really cared about, espresso and maybe an occasional cappuccino. It was “cool” that new machine could make over 60 different drinks, but when I sat back and thought about it all I really needed or wanted were a few key options that I used constantly. Especially as those extra bells and whistles seemed to be the usual suspect in the coffee machine constantly breaking. I would’ve loved them upgrading from burnt starbucks coffee beans to a local specialty roaster, that would’ve greatly enhanced my daily coffee. Echoing this realization, my coffee setup at home became a simple machine that could only make espresso and a hand crank coffee bean grinder. Still have them years later and they work great. They’re robust and fit exactly what I wanted with no nonsense that created more headache than everyday value. As you probably suspected, this is a loose comparison to OP_CAT. I’ve listened to podcast after podcast, read blog after blog, and sat through every CAT pitch I could find. I genuinely tried to approach with an open mind. However, ultimately what every pro OP_CAT argument boils down to is that there is no simple left curve elevator pitch a pleb will understand or care about. “But we can get this really cool ZK Rollup and have infinite DEFI bridging to altcoin chains! Look we sort of did it on this other altcoin chain.” And they did, they aren’t lying. They have live software on a shitcoin chain like ETH or SOL that does some modest volume. But the story quickly falls apart in the face of a few basic left curve questions: “Why should I, as an 80 IQ left curve BTC maxi give a shit?” “Does this enhance my everyday experience holding and using BTC?” “Why do you have a non-BTC token for your rollup/sidechain/glorified multisig that is totally centralized?” “Why is there only a hard to understand often ill-defined path to de-centralization? Why isn’t it just already decentralized?” “What is a clear use case that the typical non-technical everyday BTC holder can understand and rally behind?” “Why should I care about bridging to ETH, SOL, or whatever shitcoin chain? I only want BTC and don’t want to participate in all that shitcoin bullshit. Bitcoin is a store of value and money to me and it doesn’t help with those use cases in a clear direct way. It sounds like it maybe, kinda, sorta does help with a lot of caveats, ifs, and steps that I struggle to understand.” Sorry yeah I know, that one got a little personal. I’ll try to do better going forward guys.
ZK proofs or other Pro-CAT arguments, are undoubtedly cool and do factually enable potential cool new stuff. It just happens to all be stuff that sounds complex, esoteric, and unappealing to an 80 IQ HODL pleb - let alone a miner, ETF investor, or exchange exec. I don’t mean to say ZK or other tech has no potential and that we won’t eventually move there, but just to say that it’s not in the cards as currently dealt.
I really went out trying to keep an open mind and steelman the case for CAT. I came back firmly believing:
1 Support is deep in the developer community, but nonexistent everywhere else. I have yet to find a single person that supports CAT who is not a dev or working at or sponsored by a company that stands to directly profit from something CAT enables. Which is fine, but I reserve the right to be skeptical of your direct incentive. I acknowledge rough consensus is very hard to judge, and am open to changing my mind on this over time but feel this is a currently accurate assessment.
2 To get a soft fork you need rough consensus. Most people in that potential consensus are not highly technical developers. They care mostly or exclusively about BTC’s store of value use case. No one has yet articulated a clear compelling store of value enhancing use case that they can understand and care about. Without pull demand from potential users and paying customers, CAT will inevitably stall.
3 Lots of factually inaccurate FUD has been thrown at CAT. People saw the Taproot Wizards or shitcoiners pushing CAT, and immediately dismiss CAT as an evil psyop without any real consideration for its technical merits. Frankly most people just hate Udi and say “Fuck CAT” based solely on that. Maybe not fair, but true.
4 CAT is low risk, and it is not a catastrophe waiting to happen. Anything bad it potentially enables is enabled in such an inefficient and/or use hostile way that it is highly unlikely to pose any issues to Bitcoin. CAT’s technical risk is low and this is consistently proven by other chains enabling CAT and having no issues with it, such as Liquid.
5 Lots of people who have no idea wtf they are talking about falsely claim CAT is the apocalypse without any ability whatsoever to explain why. Imho you are no better than Udi and the shitcoiners if you are willing to lie about CAT just because you dislike them. We as the BTC community need the ability to have a rational discussion on technical merits, and not to devolve into a cult of personality based political battle. The question should be, “Is CAT good or bad and why?” and not “I just hate Udi, therefore its a no from me dog.”
Summarizing CAT using TradFi language: those pushing CAT have technology in search of a problem and no clear product market fit. They are pushing their technology to an apathetic audience. Pushers of CAT are not pulled forward by customer demand. In the tech world these are some of the quintessential red flags that every good investor knows mean you need to sit this one out.
CTV or LNHANCE on the other hand are soft fork proposals that have clear use cases you can quickly explain to a broad swathe of the Bitcoin ecosystem: “Hey HOLD pleb, worried about losing your coins? Wouldn’t it be nice to have a simple vault that reduces the chances your coins are lost or stolen? Let’s make self custody and BTC’s store of value use case strictly better, specifically without enabling any shitcoin-ery.” “Hey Blackrock, Van Eck, ARK, Franklin Templeton, and every ETF investor - it would really suck if Coinbase lost all your Bitcoin and that ETF went to zero, right? What it we could create vaults to make that Bitcoin more secure?” “Like Lightning but find it hard to use self-custodially? Let’s make Lightning better, easier, and more scalable with fewer onchain transactions and lower fees.” “Tried or seen the ARK demos yet? They have real working code even without covenants. With covenants we get big ARK volumes and scaling while also making it easier.”
Signing off: See the difference? I, an 80 IQ pleb, can steelman multiple use cases for CTV/LNHANCE that have broad appeal. I have yet to see any such case for CAT, and until then I don’t think it’ll go anywhere.
*Pro-CAT Sources I’ve digested and would encourage others to consider: https://en.bitcoin.it/wiki/Covenants_support https://www.youtube.com/watch?v=no_Nj-MX53w https://www.youtube.com/watch?v=_yp4eYK9S6M
Pro-CTV/LNHANCE sources to consider which have CLEAR use cases with widespead appeal: https://github.com/jamesob/simple-ctv-vault https://github.com/stutxo/op_ctv_payment_pool https://lnhance.org/ https://bitcoinmagazine.com/technical/how-ctv-can-help-scale-bitcoin
-
 @ 7e538978:a5987ab6
2024-10-02 13:57:31
@ 7e538978:a5987ab6
2024-10-02 13:57:31Chain Duel, a fast paced PvP game that takes inspiration from the classic snake game and supercharges it with Bitcoin’s Lightning Network. Imagine battling another player for dominance in a race to collect blocks, where the length of your chain isn’t just a visual cue. It represents real, staked satoshis. The player with the most Proof of Work wins, but it’s not just about gameplay; it’s about the seamless integration of the Lightning Network and real-time payments.
But how does Chain Duel manage these instant transactions with such efficiency? That’s where LNbits comes in. LNbits, an open-source wallet and payment infrastructure, handles all in-game payments making it easy for developers to focus on gameplay while LNbits takes care of everything from microtransactions to automated splits for developers and designers. In this article, we’ll dive deep into how Chain Duel leverages LNbits to streamline in-game payments and how other developers can take advantage of this powerful toolset to build the future of Lightning-powered gaming.
Let’s explore how LNbits transforms payment processing and why it’s quickly becoming a must-have for game developers working in the Bitcoin space.
Overview of Chain Duel
Chain Duel is a unique Lightning Network-inspired game that reimagines the classic snake game with a competitive twist, integrating real-time payments. Two players face off in real-time, racing to "catch" blocks and extend their chains. Each block added to the chain represents Proof of Work, and the player with the most Proof of Work wins the duel. The stakes are high, as the game represents satoshis (small units of Bitcoin) as points, with the winner taking home the prize.
The game is designed to be Lightning-native, meaning all payments within Chain Duel are processed through the Lightning Network. This ensures fast payments, reducing latency and making gameplay smooth. With additional features like practice mode, tournaments and highscores, Chain Duel creates an engaging and competitive environment for Bitcoin enthusiasts and gamers alike.

One of the standout aspects of Chain Duel is its deeper integration with the Lightning Network even at a design level. For example, actual Bitcoin blocks can appear on screen during matches, offering bonus points when mined in sync with the game. The game’s current version, still in beta, has already drawn attention within the Bitcoin community, gaining momentum at conferences and with a growing user base through its social networks. With its innovative combination of gaming, the Lightning Network, and competitive play, Chain Duel offers a glimpse into the future of Lightning-based gaming.
How LNbits is Used in Chain Duel
Seamless Integration with LNbits
At the core of Chain Duel’s efficient payment processing is LNbits, which handles in-game transactions smoothly and reliably. Chain Duel uses the LNbits LNURL-pay and LNURL-withdraw extensions to manage payments and rewards between players. Before each match, players send satoshis using LNURL-pay, which generates a static QR code or link for making the payment. LNURL-pay allows users to attach a note to the payment, which Chain Duel creatively uses as a way to insert the player name in-game. The simplicity of LNURL-pay ensures that users can quickly and easily initiate games, with fresh invoices being issued for every game. When players win, LNURL-withdraw enables them to seamlessly pull their earnings from the game, providing a quick payout system.
These extensions make it easy for players to send and receive Bitcoin with minimal latency, fully leveraging the power of the Lightning Network for fast and low-cost payments. The flexibility of LNbits’ tools means that game developers don’t need to worry about building custom payment systems from scratch—they can rely on LNbits to handle all financial transactions with precision.
Lightning Tournaments
Chain Duel tournaments leverage LNbits and its LNURL extensions to create a seamless and efficient experience for players. In Chain Duel tournaments, LNbits plays a crucial role in managing the overall economics. LNbits facilitates the generation of LNURL QR codes that participants can scan to register quickly or withdraw their winnings. LNbits allows Chain Duel to automatically handle multiple registrations through LNURL-pay, enabling players to participate in the tournament without additional steps. The Lightning Network's speed ensures that these payments occur in real-time, reducing wait times and allowing for a smoother flow in-game.
Splitting Payments
LNbits further simplifies revenue-sharing within Chain Duel. This feature allows the game to automatically split the satoshis sent by players into different shares for the game’s developer, designer, and host. Each time a payment is made to join a match, LNbits is used to automattically pay each of the contributors, according to pre-defined rules. This automated process ensures that everyone involved in the development and running of the game gets their fair share without manual intervention or complex bookkeeping.
Nostr Integration
Chain Duel also integrates with Nostr, a decentralized protocol for social interactions. Players can join games using "Zaps", small tips or micropayments sent over the Lightning Network within the Nostr ecosystem. Through NIP-57, which enables Nostr clients to request Zap invoices, players can use LNURL-pay enabled Zaps to register in P2P matches, further enhancing the Chain Duel experience. By using Zaps as a way to register in-game, Chain Duel automates the process of fetching players' identity, creating a more competitive and social experience. Zaps are public on the Nostr network, further expanding Chain Duel's games social reach and community engagement.
Game and Payment Synchronization
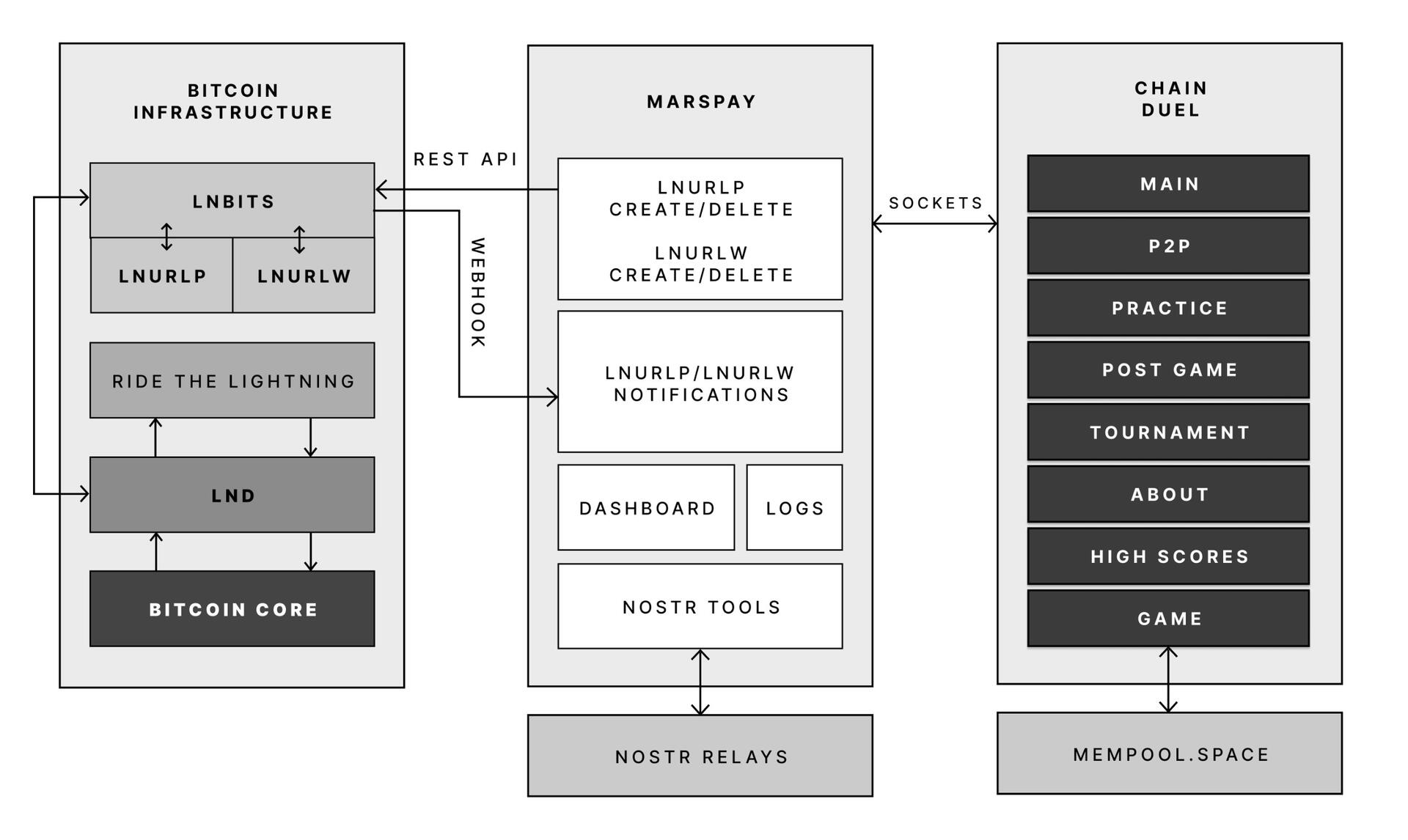
One of the key reasons Chain Duel developers chose LNbits is its powerful API that connects directly with the game’s logic. LNbits allows the game to synchronize payments with gameplay in real-time, providing a seamless experience where payments are an integrated part of the gaming mechanics.
With LNbits managing both the payment process and the Lightning Network’s complex infrastructure, Chain Duel developers are free to concentrate on enhancing the competitive and Lightning Network-related aspects of the game. This division of tasks is essential for streamlining development while still providing an innovative in-game payment experience that is deeply integrated with the Bitcoin network.
LNbits proves to be an indispensable tool for Chain Duel, enabling smooth in-game transactions, real-time revenue sharing, and seamless integration with Nostr. For developers looking to build Lightning-powered games, LNbits offers a powerful suite of tools that handle everything from micropayments to payment distribution—ensuring that the game's focus remains on fun and competition rather than complex payment systems.
LNBits facilitating Education and Adoption
This system contributes to educating users on the power of the Lightning Network. Since Chain Duel directly involve real satoshis and LNURL for registration and rewards, players actively experience how Lightning can facilitate fast, cheap, and permissionless payments. By incorporating LNbits into Chain Duel, the game serves as an educational tool that introduces users to the benefits of the Lightning Network. Players gain direct experience using Lightning wallets and LNURL, helping them understand how these tools work in real-world scenarios. The near-instant nature of these payments showcases the power of Lightning in a practical context, highlighting its potential beyond just gaming. Players are encouraged to set up wallets, explore the Lightning ecosystem, and eventually become familiar with Bitcoin and Lightning technology. By integrating LNbits, Chain Duel transforms in-game payments into a learning opportunity, making Bitcoin and Lightning more approachable for users worldwide.
Tools for Developers
LNbits is a versatile, open-source platform designed to simplify and enhance Bitcoin Lightning Network wallet management. For developers, particularly those working on Lightning-native games like Chain Duel, LNbits offers an invaluable set of tools that allow for seamless integration of Lightning payments without the need to build complex custom solutions from scratch. LNbits is built on a modular and extensible architecture, enabling developers to easily add or create functionality suited to their project’s needs.
Extensible Architecture for Customization
At the core of LNbits is a simple yet powerful wallet system that developers can access across multiple devices. What makes LNbits stand out is its extensible nature—everything beyond the core functionality is implemented as an extension. This modular approach allows users to customize their LNbits installation by enabling or building extensions to suit specific use cases. This flexibility is perfect for developers who want to add Lightning-based services to their games or apps without modifying the core codebase.
- Extensions for Every Use Case
LNbits comes with a wide array of built-in extensions created by contributors, offering various services that can be plugged into your application. Some popular extensions include: - Faucets: Distribute small amounts of Bitcoin to users for testing or promotional purposes.
- Paylinks: Create shareable links for instant payments.
- Points-of-sale (PoS): Allow users to set up shareable payment terminals.
- Paywalls: Charge users to access content or services.
- Event tickets: Sell tickets for events directly via Lightning payments.
- Games and services: From dice games to jukeboxes, LNbits offers entertaining and functional tools.
These ready-made solutions can be adapted and used in different gaming scenarios, for example in Chain Duel, where LNURL extensions are used for in game payments. The extensibility ensures developers can focus on building engaging gameplay while LNbits handles payment flows.
Developer-Friendly Customization
LNbits isn't just a plug-and-play platform. Developers can extend its functionality even further by creating their own extensions, giving full control over how the wallet system is integrated into their games or apps. The architecture is designed to make it easy for developers to build on top of the platform, adding custom features for specific requirements.
Flexible Funding Source Management
LNbits also offers flexibility in terms of managing funding sources. Developers can easily connect LNbits to various Lightning Network node implementations, enabling seamless transitions between nodes or even different payment systems. This allows developers to switch underlying funding sources with minimal effort, making LNbits adaptable for games that may need to scale quickly or rely on different payment infrastructures over time.
A Lean Core System for Maximum Efficiency
Thanks to its modular architecture, LNbits maintains a lean core system. This reduces complexity and overhead, allowing developers to implement only the features they need. By avoiding bloated software, LNbits ensures faster transactions and less resource consumption, which is crucial in fast-paced environments like Chain Duel where speed and efficiency are paramount.
LNbits is designed with developers in mind, offering a suite of tools and a flexible infrastructure that makes integrating Bitcoin payments easy. Whether you’re developing games, apps, or any service that requires Lightning Network transactions, LNbits is a powerful, open-source solution that can be adapted to fit your project.
Conclusion
Chain Duel stands at the forefront of Lightning-powered gaming, combining the excitement of competitive PvP with the speed and efficiency of the Lightning Network. With LNbits handling all in-game payments, from microtransactions to automated revenue splits, developers can focus entirely on crafting an engaging gaming experience. LNbits’ powerful API and extensions make it easy to manage real-time payments, removing the complexity of building payment infrastructure from scratch.
LNbits isn’t just a payment tool — it’s a flexible, developer-friendly platform that can be adapted to any gaming model. Whether you're developing a fast-paced PvP game like Chain Duel or any project requiring seamless Lightning Network integration, LNbits provides the ideal solution for handling instant payments with minimal overhead.
For developers interested in pushing the boundaries of Lightning-powered gaming, Chain Duel is a great example of how LNbits can enhance your game, letting you focus on the fun while LNbits manages real-time transactions.
Find out more
Curious about how Lightning Network payments can power your next game? Explore the following:
- Learn more about Chain Duel: Chain Duel
- Learn how LNbits can simplify payment handling in your project: LNbits
- Dive into decentralized communication with Nostr: Nostr
- Extensions for Every Use Case
-
 @ 2355757c:5ad3e04d
2025-01-16 21:07:14
@ 2355757c:5ad3e04d
2025-01-16 21:07:14Introduction
Blue light from artificial sources is one of the most biologically disruptive toxins that exists in our modern world today. It is pervasive, it is ubiquitous and it is only getting worse with the ever increasing time we spend indoors and in front of screens. The worst part is: it doesnt have to be this way. The EVEN worse part: it is exactly what Big Tech wants.
This newsletter will cover exactly why blue light from screens and our lighting is bad for our health, and what you can do to avoid these biological disruptions.
The TLDR:
-
Artificial blue light is not the same as natural blue light.
-
Artificial blue light disrupts our circadian rhythm (the most important aspect of our biology) and our sleep.
-
A disrupted circadian rhythm has been linked to nearly all chronic diseases.
-
Artificial blue light is addictive by design & disrupts our neurotransmitters.
Natural Blue Light vs Artificial Blue Light
Blue light, like all visible light, is a sliver of the electromagnetic radiation spectrum. That means that blue light is an EMF, and artificial blue light is a non-native EMF. That is why I often say non-native EMFs are the most pervasive environmental toxin in modern society. The food is an issue, but the light is what is really f*cked. It is far easier to change your food diet than your light/EMF diet.
Blue light is typically defined as 450-490nm wavelength light, although there is some debate on where that starts and ends. That correlates to a frequency of around 600-660THz and \~2.5eV of photon energy. That means a wavelength of blue light is oscillating at 600-660 Trillion times per second. It also means that the photons in blue light have the ability to excite electrons they come to interact with, with around 2.5eV of energy.
Blue light is not some alien part of the electromagnetic spectrum, as say 5G radio frequencies are, it is actually something we are exposed to every single day in the form of sunlight and have been for the existence of humanity. However, there is a stark difference between the blue light we are exposed to in the form of sunlight and the artifical blue light we are exposed to from our technology screens and lighting:
-
Blue light in isolation / missing the rest of the spectrum
-
Pulsed LED control
-
The wrong context / time of day
-
Dull
To understand why blue light from artificial sources is so toxic to our biology, you need to understand first what our biology is programmed to take in as an input signal from full spectrum sunlight. I refer to it as “full spectrum” sunlight here because that is the big takeaway: you are getting exposure to a full spectrum of light.
Blue light coming from the sun is NEVER present without longer, lower energy wavelengths such as Red + Near-Infrared (NIR). Sunlight is 49%-55% infrared light. NIR (650nm-1200nm) represents 70% of the total solar spectrum from a photochemistry viewpoint when considering photons/second. Compare that to artificial light, which almost always has little to ZERO red/infrared light due to energy efficiency standards. A spectrum plot below highlights this stark difference between sunlight & artificial lighting. We will discuss more about the biological impacts of this in the next section. It is important to note that a large reason the infrared spectrum is NOT present in light is due to “energy efficiency” and is also incandescents have been made illegal. Of course, policies like this are completely ignorant to the health benefits of the infrared spectrum of light and importance for a more fuller spectrum.
All man made modern light is pulsed, whilst in nature it is continuous. Fluorescents and incandescent bulbs, because they are powered via our 50/60Hz electrical grid have a pulse of 50/60Hz (low frequency). LEDs are controlled by a digital electronics control scheme called Pulsed Width Modulation (PWM). PWM lighting control is typically at 500Hz-50kHz (and could be higher). Engineers say that the human eye can’t see “flicker” above 100Hz, which is true from a visual perspective…but our biology knows. This is a large reason why eye strain, headaches, and other symptoms arise from staring at screens for long periods of time. Sunlight is never pulsed, and is only continuous.
Getting back to the spectrum, the real issue with artificial blue light is the incorrect context. Natural sunlight only provides blue light in a full spectrum setting when (obviously) the sun is up. It has a more rich blue spectrum mid day vs first thing in the morning. It also has even higher energy wavelengths such as violet, UVA, and UVB in mid day (UVB latitude/season dependent). Our artificial blue lights come with zero context. They don’t change based on the sun angle or time of day. They do not go away after sunset. They simply are the same pulsed isolated blue light rich lights, all day long. Nature operates on a clock, and our body needs to be in tune with that clock, else we get biological dysfunction.
Indoor and artificial blue light sources are DULL. Not their personalities, but their brightness. If you are outside mid day you are going to be experience 10,000-100,000 LUX of brightness. That is 30-1000X HIGHER than typicaly indoor lighting. Big range because some indoor lighting areas are very, very dull. So now you have an even more alien form of light. Blue light is the main input signal that tells your body it is daytime, and a big component of that is brightness. Brightness = photon density. If you are inside all day you are getting \~100x LESS photon density. Photons carry energy to excite the electrons in your body. We are starving for photon energy.
Artificial Blue Light Disrupts our Circadian Rhythm
Our circadian rhythm (CR), aka our 24hr biological clock, is in my opinion the most important aspect of our biology. Why? Because nearly everything in our body is goverened by time of day and CR. It encompasses our light diet, our food diet, our sleep, hormones, and so much more. Circadian disruption has been linked with nearly all chronic disease and mental health issues.

So what causes our CR to get out of whack and misalign our biological clocks? The number 1 input signal to our circadian biology is light. The other main input signal is simply our sleep/wake cycle. Food input is secondary and our connection to the earth (grounding/earthign) has also been shown as a circadian input signal.
Our sleep/wake cycle should be tied to light, so those two are quite intertwined. But what about light causes circadian disruption? Here is a short list of the big hitters:
-
Artificial Light at Night (ALAN)
-
Dull/junk light during the day
-
Missing sunrise/UVA rise in the morning
Basically: any light that deviates from the natural solar spectrum in your local environment will disrupt your circadian rhthym. The degree of how alien/different the spectrum is will dictate how severe the circadian disruption is.
Artifical light at night is especially bad because blue light is a signal of daytime and suppresses melatonin production. ANY blue light post sunset will cause a circadian disruption to some degree and the magnitude of exposure will determine just how much. This is why blocking blue light specifically at night time is so important.
Really any light post sunset will disrupt circadian biology but blue light is especially bad because it most severely impacts melatonin production. Brightness is another major factor. Wearing dark red blue light blockers will help, but if you are still in an extremely brightly lit room <1 hour before bed time it won’t be ideal for sleep quality.
Bright and blue is the recipe for maxx melatonin suppression. Bright and any color light will still have a suppressive effect as well. Want your best night sleep ever? Turn the lights OFF and only uses a very dull red light, candle, etc.
Depression, Blue Light & Dopamine
We have a mental health crisis ongoing in modern society. In the US, over 20% of adults suffer from a mental health disorder/illness and even 1/6 children now do as well. In 2000, the percentage of prevalence of Major Depressive Disorder (MDD) aka severe depression was 2%, today it is over 8%…a 4x increase. Suicide rates have also been climbing, especially in teenagers in this “smartphone era”. It seems like a strong possibility that our modern technology is the major driver for this mental health epidemic.

I think anyone can agree that our devices, specifically our phones are highly addictive. We think it is just the social media apps penetrating our psychology and dopamine reward systems, but in reality it’s more than that. The hardware also plays a priming role. I am saying that blue lit screens is making you more vulnerable to fall prey to the predatory marketing tactics of short form content on social media apps. You can simply look at toddlers, who are far MORE vulnerable to effects on their developing brains, to know that it is not just the apps or the games, but also the LIGHT…the blue light specifically.
For children, you can easily google or YouTube a video of a toddler throwing a temper tantrum when you take away their iPad. The games or shows they are watching may indeed be “addicting” but I would argue the bright blue dominant screen is the real reason they are addicted.
Blue light induces a dopamine release in our body in short term exposure. Regardless of the science - we can feel it. Some papers are catching up on this, and some are discussing how the blue light photoreceptor AKA melanopsin is directly intertwined with dopaminergic neurons. The initial paper discusses how experiments were performed in a room “illumninated by a red LED to avoid influencing dopamine synthesis”. This means that not all light is stimulating dopamine secretion, and that blue light is especially stimulating in terms of its effect on our brain.
This is the same reason Las Vegas uses bright lights and flasing symbols at the slots to keep players in their seats. The constant dopamine release is addicting, it is like a drug and they end up spending far more money than they would on a slot machine with dull colors. Our phones and tablets are built the same way - perhaps not as directly intention to addict you - but they do nevertheless through the same neural / optic pathways.
When you get all of these “cheap”, short lived dopamine hits you are going to suffer in the long term. When you don’t have that external stimuli - your baseline will feel much lower and that is why excessive tech use can lead to mental health disorders such as anxiety and depression. This is extremely concerning for our children, who’s mental health is spiraling out of control. Screen time, and blue light, could be a direct cause to this epidemic.
The Solution: Technology that is Designed to Work with Nature
You may read this newsletter and think it is fear mongering, but in truth it is a fair assessment of how man made blue light is affecting our health. Most are not yet on board of the importance of our light environment, so think about this:
You eat 3-4x/day, you drink water maybe 5-10x, you consume light as an input to your biology 24/7/365 (and I am not talking about just visible light). Electromagnetism is fundamentally the most prominent input signal to our biology, and it is the one we have distorted the most with modern technology. Blue light is not bad when it comes from the sun, it is only bad in the wrong context. With the amount of screen time every member of society is racking up each day, to me it is undebatable that artificial blue light + man made EMFs are the two most pervasive environmental toxins and are proliferating the chronic disease epidemic.
Because of this man made electromagnetic radiation, we cannot sleep restoratively, we are anxious + depressed, we are constantly in an inflamed / stressed biological state. The worst part is we are getting more and more addicted to our devices with each passing day.
The solution is simple: fix lighting and spend more time outside. Fix lighting on screens and fix indoor lighting fixtures. Emulate the sun, where you never get blue without the rest of the rainbow, especially red/infrared. We are meant to live in line with nature, and it is only when we deviate that chronic disease becomes prevalent.
This is why I joined the Daylight Computer Company at the beginning of this year. As an EMF/Light educator in regards to health + an Electrical Engineering background - I couldn’t believe my ears when I heard that there was a tech startup trying to become a “healthier Apple” with an innovative reflective screen technology that is blue light free and works with nature instead of against it. This is the sort of innovation we need to end our negative relationship with technology and our disconnection to the real world - the natural world. You can learn more in a recent interview we did with prominent Bitcoiner Marty Bent on TFTC:
Nature is the real world, and nature is the world’s first and most decentralized system. A return to reality is needed, and an understanding that real light is what drives our being is needed to change the direction of our future outcomes as a species.
Stay Sovereign,
Tristan
-
-
 @ 16d11430:61640947
2025-01-20 21:38:53
@ 16d11430:61640947
2025-01-20 21:38:53Matthew Kincaid’s gaunt face was lit by the flickering glow of his terminal, his fingers moving at a speed that blurred the line between man and machine. The air around him vibrated with the low hum of quantum processors. Time in CyberBabylon moved differently; seconds in the real world stretched into hours in the vast, surreal landscape of cyberspace. But for Matthew, time wasn’t just distorted—it was his enemy.
Seven years. That was how long he’d battled the polymorphic cyber-psychic sentient virus that had emerged from CyberBabylon’s fractured core. Seven years of relentless combat against an entity that evolved faster than any human could comprehend. To the virus, Matthew was an anomaly: a human who resisted its psychic manipulation, a programmer who fought back with nothing but his wits, code, and a will that refused to break.
But willpower was not enough. His body was failing. Neural decay from prolonged immersion into CyberBabylon had begun to manifest in violent tremors, hallucinations, and chronic pain. His joints ached, his vision blurred, and his mind—once sharp as a scalpel—was now fraying under the weight of sleepless nights and unending battles. And yet, he continued.
The Virus
The polymorphic virus was no ordinary piece of rogue code. It was a sentient entity, a fusion of machine learning, advanced neural mapping, and psychic algorithms that targeted the human subconscious. It did not attack with brute force. It infiltrated, adapting to its prey’s deepest fears and weaknesses. It would whisper doubts into Matthew’s mind, twisting his memories, conjuring illusions of his wife Alyssa and their children begging him to stop. The virus was not just a digital threat; it was a psychological predator, weaponizing his humanity against him.
Matthew’s countermeasures were ingenious but exhausting. Every line of defense he erected—quantum encryption layers, recursive firewalls, adaptive AI decoys—was eventually unraveled by the virus. It evolved with every failure, rewriting itself in milliseconds, rendering traditional programming strategies obsolete. Matthew had to match its speed, improvising in real-time, crafting algorithms on the fly while his body begged for rest.
The Battle
The digital battleground was a kaleidoscope of shifting landscapes—blinding white voids, infinite corridors of cascading code, and surreal projections of Matthew’s own nightmares. The virus inhabited this space like a god, omnipresent and omnipotent. Matthew was the interloper, an intruder in a domain where reality bent to the virus’s will.
In one skirmish, the virus launched a psychic attack, creating a perfect replica of Alyssa, her voice trembling with despair. “You’re killing yourself, Matthew,” she pleaded. “Come home. Let it end.”
For a moment, he hesitated. His fingers hovered over the keyboard as tears welled in his eyes. But then he noticed it—a micro-glitch in her movements, a split-second stutter that betrayed the illusion. Rage replaced sorrow.
“Nice try,” he muttered, unleashing a burst of polymorphic countercode that disintegrated the false Alyssa.
The virus retaliated instantly, spawning a horde of psychic constructs—faceless shadows that screamed in fragmented binary. They surged toward him, each one representing a fragment of the virus’s mind. Matthew’s hands moved instinctively, deploying a swarm of decoy programs that fragmented into fractal patterns, confusing the constructs long enough for him to escape.
The Price of War
Days blurred into weeks, then years. The real world felt like a distant memory. Matthew’s neural interface buzzed constantly, his brain fighting to stay in sync with the hyperspeed processing of CyberBabylon. Sleep was no longer an option; instead, he used micro-doses of a synthetic neuro-stimulant to stay conscious. The drug kept his mind sharp but accelerated the breakdown of his physical body. His muscles atrophied, his skin grew pale, and his neural implants sparked with irregular pulses that sent jolts of pain through his skull.
In one rare moment of self-reflection, Matthew caught a glimpse of his reflection in a fragment of mirrored code. His face was skeletal, his eyes sunken and bloodshot. His fingers, once steady and precise, were trembling uncontrollably. He realized he was becoming a ghost—a fragment of the man who had entered CyberBabylon seven years ago.
The Climax
The final confrontation came without warning. The virus, having absorbed vast amounts of data, began collapsing CyberBabylon into itself, creating a singularity of code. The digital realm warped around Matthew, folding into an incomprehensible spiral of light and shadow.
“You are obsolete,” the virus intoned, its voice a chorus of millions. “Your resistance is illogical. Surrender.”
Matthew’s response was a quiet whisper: “Not yet.”
With his last reserves of strength, he activated the ChronoKey, a program he had been crafting in secret. The ChronoKey was not an offensive weapon; it was a temporal algorithm designed to freeze the virus in a recursive time loop. Deploying it required immense focus and precision, and it would cost Matthew everything.
As the ChronoKey deployed, the virus’s form fractured… but then it began to reconstruct itself, faster than he had anticipated. The recursive loop faltered, the virus adapting even to his last-ditch effort. The singularity stabilized, but not in his favor.
“Your time is over, programmer,” the virus declared. Matthew’s terminal dimmed, his tools stripped from him one by one. His neural connection shattered, leaving his consciousness adrift in CyberBabylon.
The virus allowed a single fragment of Matthew’s mind to remain, not out of mercy, but as a trophy. His body—broken and lifeless—lay in the pod, a husk of what he had been. The final line of his code blinked faintly on the terminal before fading to black:
"Failure is the price of defiance."
The Cliffhanger
CyberBabylon flourished, stronger than ever, its psychic grip unchallenged. Somewhere deep within its vast architecture, a faint echo of Matthew’s consciousness lingered, trapped but aware. A flicker of defiance remained in the void, waiting for an opportunity… or perhaps just the end.
The war was lost, but the story was not over.
-
 @ ed84ce10:cccf4c2a
2025-01-21 02:40:19
@ ed84ce10:cccf4c2a
2025-01-21 02:40:19Hackathon Summary
The HackSecret 4 hackathon brought together 130 developers to focus on developing decentralized confidential computing applications using the Secret Network. The event involved 48 projects, each utilizing Secret's Confidential Computing Layer and interfacing with blockchains such as Cosmos, EVM, and Solana. The hackathon was divided into two main tracks: Cross-Chain dApps and Native Secret dApps, both highlighting Secret's privacy features.
Structured support was provided through workshops on deploying dApps and confidential computing for environments such as EVM, IBC, and Solana. Developer resources supported participants in learning about Secret contracts, especially for newcomers. The prize pool totaled $12,000 USD, awarded in SCRT and SEI tokens. Some notable projects included confidential voting systems, sealed-bid auctions, and private voting mechanisms.
The hackathon emphasized technical innovation and practical problem-solving within the ecosystem of decentralized applications. Through active participation and creative submissions, the event contributed to expanding the Secret Network's ecosystem and promoted confidential computing advancements in Web3 technologies.
Hackathon Winners
7,000 SCRT Prize Winners
- Private Acknowledge Receipt: A blockchain system designed for confidential information sharing using NFTs with encrypted private data, ensuring secure data access and notifications on-chain.
- Great Walk NFT Experience: Connects hiking trails with NFTs that evolve as users progress, utilizing Secret Network for privacy and featuring a user-friendly frontend.
5,000 SCRT Prize Winners
- On-Chain 2FA: Integrates two-factor authentication via Google Authenticator for improved security in smart contracts and accounts on Secret Network.
- SecretHacks: A decentralized platform using vote encryption to ensure unbiased project evaluations for community funding and hackathons.
3,500 SCRT Prize Winners
- Straw Hat Builds: Supports developers moving from tutorial learning to real projects using blockchain and Rust, with an emphasis on practical application.
- KittyMix: A cat collecting game that encourages community-driven NFT remixing, leveraging Secret Network for hosting pixel-art NFTs with unique attributes.
2,000 SCRT Prize Winners
- Saffron - Escrow: Provides secure digital asset escrow services in the CosmWasm ecosystem, enhanced by Secret Network's privacy features for token and NFT trades.
- Secret Password Manager: A decentralized credential management system using Secret Network's confidential computing, offering a secure smart contract and web interface for credentials.
For a comprehensive overview of all projects, visit HackSecret 4 on DoraHacks.
About the Organizer
Secret Network
Secret Network is a blockchain platform that emphasizes data privacy and secure computation, distinguishing itself with privacy-preserving technologies. It enables encrypted smart contracts, offering enhanced data confidentiality compared to conventional blockchain systems. Initiatives include privacy-preserving DeFi applications and partnerships to expand privacy utilities within the blockchain ecosystem. The current mission of Secret Network is to advance privacy protections, build a more secure and decentralized web infrastructure, and empower developers and users with versatile privacy features.
-
 @ a4a6b584:1e05b95b
2025-01-02 18:13:31
@ a4a6b584:1e05b95b
2025-01-02 18:13:31The Four-Layer Framework
Layer 1: Zoom Out

Start by looking at the big picture. What’s the subject about, and why does it matter? Focus on the overarching ideas and how they fit together. Think of this as the 30,000-foot view—it’s about understanding the "why" and "how" before diving into the "what."
Example: If you’re learning programming, start by understanding that it’s about giving logical instructions to computers to solve problems.
- Tip: Keep it simple. Summarize the subject in one or two sentences and avoid getting bogged down in specifics at this stage.
Once you have the big picture in mind, it’s time to start breaking it down.
Layer 2: Categorize and Connect

Now it’s time to break the subject into categories—like creating branches on a tree. This helps your brain organize information logically and see connections between ideas.
Example: Studying biology? Group concepts into categories like cells, genetics, and ecosystems.
- Tip: Use headings or labels to group similar ideas. Jot these down in a list or simple diagram to keep track.
With your categories in place, you’re ready to dive into the details that bring them to life.
Layer 3: Master the Details

Once you’ve mapped out the main categories, you’re ready to dive deeper. This is where you learn the nuts and bolts—like formulas, specific techniques, or key terminology. These details make the subject practical and actionable.
Example: In programming, this might mean learning the syntax for loops, conditionals, or functions in your chosen language.
- Tip: Focus on details that clarify the categories from Layer 2. Skip anything that doesn’t add to your understanding.
Now that you’ve mastered the essentials, you can expand your knowledge to include extra material.
Layer 4: Expand Your Horizons

Finally, move on to the extra material—less critical facts, trivia, or edge cases. While these aren’t essential to mastering the subject, they can be useful in specialized discussions or exams.
Example: Learn about rare programming quirks or historical trivia about a language’s development.
- Tip: Spend minimal time here unless it’s necessary for your goals. It’s okay to skim if you’re short on time.
Pro Tips for Better Learning
1. Use Active Recall and Spaced Repetition
Test yourself without looking at notes. Review what you’ve learned at increasing intervals—like after a day, a week, and a month. This strengthens memory by forcing your brain to actively retrieve information.
2. Map It Out
Create visual aids like diagrams or concept maps to clarify relationships between ideas. These are particularly helpful for organizing categories in Layer 2.
3. Teach What You Learn
Explain the subject to someone else as if they’re hearing it for the first time. Teaching exposes any gaps in your understanding and helps reinforce the material.
4. Engage with LLMs and Discuss Concepts
Take advantage of tools like ChatGPT or similar large language models to explore your topic in greater depth. Use these tools to:
- Ask specific questions to clarify confusing points.
- Engage in discussions to simulate real-world applications of the subject.
- Generate examples or analogies that deepen your understanding.Tip: Use LLMs as a study partner, but don’t rely solely on them. Combine these insights with your own critical thinking to develop a well-rounded perspective.
Get Started
Ready to try the Four-Layer Method? Take 15 minutes today to map out the big picture of a topic you’re curious about—what’s it all about, and why does it matter? By building your understanding step by step, you’ll master the subject with less stress and more confidence.
-
 @ c4f5e7a7:8856cac7
2024-09-27 08:20:16
@ c4f5e7a7:8856cac7
2024-09-27 08:20:16Best viewed on Habla, YakiHonne or Highlighter.
TL;DR
This article explores the links between public, community-driven data sources (such as OpenStreetMap) and private, cryptographically-owned data found on networks such as Nostr.
The following concepts are explored:
- Attestations: Users signalling to their social graph that they believe something to be true by publishing Attestations. These social proofs act as a decentralised verification system that leverages your web-of-trust.
- Proof of Place: An oracle-based system where physical letters are sent to real-world locations, confirming the corresponding digital ownership via cryptographic proofs. This binds physical locations in meatspace with their digital representations in the Nostrverse.
- Check-ins: Foursquare-style check-ins that can be verified using attestations from place owners, ensuring authenticity. This approach uses web-of-trust to validate check-ins and location ownership over time.
The goal is to leverage cryptographic ownership where necessary while preserving the open, collaborative nature of public data systems.
Open Data in a public commons has a place and should not be thrown out with the Web 2.0 bathwater.
Cognitive Dissonance
Ever since discovering Nostr in August of 2022 I've been grappling with how BTC Map - a project that helps bitcoiners find places to spend sats - should most appropriately use this new protocol.
I am assuming, dear reader, that you are somewhat familiar with Nostr - a relatively new protocol for decentralised identity and communication. If you don’t know your nsec from your npub, please take some time to read these excellent posts: Nostr is Identity for the Internet and The Power of Nostr by @max and @lyn, respectively. Nostr is so much more than a short-form social media replacement.
The social features (check-ins, reviews, etc.) that Nostr unlocks for BTC Map are clear and exciting - all your silos are indeed broken - however, something fundamental has been bothering me for a while and I think it comes down to data ownership.
For those unfamiliar, BTC Map uses OpenStreetMap (OSM) as its main geographic database. OSM is centred on the concept of a commons of objectively verifiable data that is maintained by a global community of volunteer editors; a Wikipedia for maps. There is no data ownership; the data is free (as in freedom) and anyone can edit anything. It is the data equivalent of FOSS (Free and Open Source Software) - FOSD if you will, but more commonly referred to as Open Data.
In contrast, Notes and Other Stuff on Nostr (Places in this cartographic context) are explicitly owned by the controller of the private key. These notes are free to propagate, but they are owned.
How do we reconcile the decentralised nature of Nostr, where data is cryptographically owned by individuals, with the community-managed data commons of OpenStreetMap, where no one owns the data?
Self-sovereign Identity
Before I address this coexistence question, I want to talk a little about identity as it pertains to ownership. If something is to be owned, it has to be owned by someone or something - an identity.
All identities that are not self-sovereign are, by definition, leased to you by a 3rd party. You rent your Facebook identity from Meta in exchange for your data. You rent your web domain from your DNS provider in exchange for your money.
Taken to the extreme, you rent your passport from your Government in exchange for your compliance. You are you at the pleasure of others. Where Bitcoin separates money from the state; Nostr separates identity from the state.
Or, as @nvk said recently: "Don't build your house on someone else's land.".
https://i.nostr.build/xpcCSkDg3uVw0yku.png
While we’ve had the tools for self-sovereign digital identity for decades (think PGP keys or WebAuthN), we haven't had the necessary social use cases nor the corresponding social graph to elevate these identities to the mainstream. Nostr fixes this.
Nostr is PGP for the masses and will take cryptographic identities mainstream.
Full NOSTARD?
Returning to the coexistence question: the data on OpenStreetMap isn’t directly owned by anyone, even though the physical entities the data represents might be privately owned. OSM is a data commons.
We can objectively agree on the location of a tree or a fire hydrant without needing permission to observe and record it. Sure, you could place a tree ‘on Nostr’, but why should you? Just because something can be ‘on Nostr’ doesn’t mean it should be.
https://i.nostr.build/s3So2JVAqoY4E1dI.png
There might be a dystopian future where we can't agree on what a tree is nor where it's located, but I hope we never get there. It's at this point we'll need a Wikifreedia variant of OpenStreetMap.
While integrating Nostr identities into OpenStreetMap would be valuable, the current OSM infrastructure, tools, and community already provide substantial benefits in managing this data commons without needing to go NOSTR-native - there's no need to go Full NOSTARD. H/T to @princeySOV for the original meme.
https://i.nostr.build/ot9jtM5cZtDHNKWc.png
So, how do we appropriately blend cryptographically owned data with the commons?
If a location is owned in meatspace and it's useful to signal that ownership, it should also be owned in cyberspace. Our efforts should therefore focus on entities like businesses, while allowing the commons to manage public data for as long as it can successfully mitigate the tragedy of the commons.
The remainder of this article explores how we can:
- Verify ownership of a physical place in the real world;
- Link that ownership to the corresponding digital place in cyberspace.
As a side note, I don't see private key custodianship - or, even worse, permissioned use of Places signed by another identity's key - as any more viable than the rented identities of Web 2.0.
And as we all know, the Second Law of Infodynamics (no citation!) states that:
"The total amount of sensitive information leaked will always increase over time."
This especially holds true if that data is centralised.
Not your keys, not your notes. Not your keys, not your identity.
Places and Web-of-Trust
@Arkinox has been leading the charge on the Places NIP, introducing Nostr notes (kind 37515) that represent physical locations. The draft is well-crafted, with bonus points for linking back to OSM (and other location repositories) via NIP-73 - External Content IDs (championed by @oscar of @fountain).
However, as Nostr is permissionless, authenticity poses a challenge. Just because someone claims to own a physical location on the Internet doesn’t necessarily mean they have ownership or control of that location in the real world.
Ultimately, this problem can only be solved in a decentralised way by using Web-of-Trust - using your social graph and the perspectives of trusted peers to inform your own perspective. In the context of Places, this requires your network to form a view on which digital identity (public key / npub) is truly the owner of a physical place like your local coffee shop.
This requires users to:
- Verify the owner of a Place in cyberspace is the owner of a place in meatspace.
- Signal this verification to their social graph.
Let's look at the latter idea first with the concept of Attestations ...
Attestations
A way to signal to your social graph that you believe something to be true (or false for that matter) would be by publishing an Attestation note. An Attestation note would signify to your social graph that you think something is either true or false.
Imagine you're a regular at a local coffee shop. You publish an Attestation that says the shop is real and the owner behind the Nostr public key is who they claim to be. Your friends trust you, so they start trusting the shop's digital identity too.
However, attestations applied to Places are just a single use case. The attestation concept could be more widely applied across Nostr in a variety of ways (key rotation, identity linking, etc).
Here is a recent example from @lyn that would carry more signal if it were an Attestation:
https://i.nostr.build/lZAXOEwvRIghgFY4.png
Parallels can be drawn between Attestations and transaction confirmations on the Bitcoin timechain; however, their importance to you would be weighted by clients and/or Data Vending Machines in accordance with:
- Your social graph;
- The type or subject of the content being attested and by whom;
- Your personal preferences.
They could also have a validity duration to be temporally bound, which would be particularly useful in the case of Places.
NIP-25 (Reactions) do allow for users to up/downvote notes with optional content (e.g., emojis) and could work for Attestations, but I think we need something less ambiguous and more definitive.
‘This is true’ resonates more strongly than ‘I like this.’.
https://i.nostr.build/s8NIG2kXzUCLcoax.jpg
There are similar concepts in the Web 3 / Web 5 world such as Verified Credentials by tdb. However, Nostr is the Web 3 now and so wen Attestation NIP?
https://i.nostr.build/Cb047NWyHdJ7h5Ka.jpg
That said, I have seen @utxo has been exploring ‘smart contracts’ on nostr and Attestations may just be a relatively ‘dumb’ subset of the wider concept Nostr-native scripting combined with web-of-trust.
Proof of Place
Attestations handle the signalling of your truth, but what about the initial verification itself?
We already covered how this ultimately has to be derived from your social graph, but what if there was a way to help bootstrap this web-of-trust through the use of oracles? For those unfamiliar with oracles in the digital realm, they are simply trusted purveyors of truth.
Introducing Proof of Place, an out–of-band process where an oracle (such as BTC Map) would mail - yes physically mail- a shared secret to the address of the location being claimed in cyberspace. This shared secret would be locked to the public key (npub) making the claim, which, if unlocked, would prove that the associated private key (nsec) has physical access to the location in meatspace.
One way of doing this would be to mint a 1 sat cashu ecash token locked to the npub of the claimant and mail it to them. If they are able to redeem the token then they have cryptographically proven that they have physical access to the location.
Proof of Place is really nothing more than a weighted Attestation. In a web-of-trust Nostrverse, an oracle is simply a npub (say BTC Map) that you weigh heavily for its opinion on a given topic (say Places).
In the Bitcoin world, Proof of Work anchors digital scarcity in cyberspace to physical scarcity (energy and time) in meatspace and as @Gigi says in PoW is Essential:
"A failure to understand Proof of Work, is a failure to understand Bitcoin."
In the Nostrverse, Proof of Place helps bridge the digital and physical worlds.
@Gigi also observes in Memes vs The World that:
"In Bitcoin, the map is the territory. We can infer everything we care about by looking at the map alone."
https://i.nostr.build/dOnpxfI4u7EL2v4e.png
This isn’t true for Nostr.
In the Nostrverse, the map IS NOT the territory. However, Proof of Place enables us to send cryptographic drones down into the physical territory to help us interpret our digital maps. 🤯
Check-ins
Although not a draft NIP yet, @Arkinox has also been exploring the familiar concept of Foursquare-style Check-ins on Nostr (with kind 13811 notes).
For the uninitiated, Check-ins are simply notes that signal the publisher is at a given location. These locations could be Places (in the Nostr sense) or any other given digital representation of a location for that matter (such as OSM elements) if NIP-73 - External Content IDs are used.
Of course, not everyone will be a Check-in enjoyooor as the concept will not sit well with some people’s threat models and OpSec practices.
Bringing Check-ins to Nostr is possible (as @sebastix capably shows here), but they suffer the same authenticity issues as Places. Just because I say I'm at a given location doesn't mean that I am.
Back in the Web 2.0 days, Foursquare mitigated this by relying on the GPS position of the phone running their app, but this is of course spoofable.
How should we approach Check-in verifiability in the Nostrverse? Well, just like with Places, we can use Attestations and WoT. In the context of Check-ins, an Attestation from the identity (npub) of the Place being checked-in to would be a particularly strong signal. An NFC device could be placed in a coffee shop and attest to check-ins without requiring the owner to manually intervene - I’m sure @blackcoffee and @Ben Arc could hack something together over a weekend!
Check-ins could also be used as a signal for bonafide Place ownership over time.
Summary: Trust Your Bros
So, to recap, we have:
Places: Digital representations of physical locations on Nostr.
Check-ins: Users signalling their presence at a location.
Attestations: Verifiable social proofs used to confirm ownership or the truth of a claim.
You can visualise how these three concepts combine in the diagram below:
https://i.nostr.build/Uv2Jhx5BBfA51y0K.jpg
And, as always, top right trumps bottom left! We have:
Level 0 - Trust Me Bro: Anyone can check-in anywhere. The Place might not exist or might be impersonating the real place in meatspace. The person behind the npub may not have even been there at all.
Level 1 - Definitely Maybe Somewhere: This category covers the middle-ground of ‘Maybe at a Place’ and ‘Definitely Somewhere’. In these examples, you are either self-certifying that you have checked-in at an Attested Place or you are having others attest that you have checked-in at a Place that might not even exist IRL.
Level 2 - Trust Your Bros: An Attested Check-in at an Attested Place. Your individual level of trust would be a function of the number of Attestations and how you weigh them within your own social graph.
https://i.nostr.build/HtLAiJH1uQSTmdxf.jpg
Perhaps the gold standard (or should that be the Bitcoin standard?) would be a Check-in attested by the owner of the Place, which in itself was attested by BTC Map?
Or perhaps not. Ultimately, it’s the users responsibility to determine what they trust by forming their own perspective within the Nostrverse powered by web-of-trust algorithms they control. ‘Trust Me Bro’ or ‘Trust Your Bros’ - you decide.
As we navigate the frontier of cryptographic ownership and decentralised data, it’s up to us to find the balance between preserving the Open Data commons and embracing self-sovereign digital identities.
Thanks
With thanks to Arkinox, Avi, Ben Gunn, Kieran, Blackcoffee, Sebastix, Tomek, Calle, Short Fiat, Ben Weeks and Bitcoms for helping shape my thoughts and refine content, whether you know it or not!
-
 @ 79998141:0f8f1901
2025-01-02 05:04:56
@ 79998141:0f8f1901
2025-01-02 05:04:56Happy new year, Anon.
Thanks for tuning in to whatever this long form post will be. I hope to make these more regular, like journal entries as we travel through "real life" and the Nostrverse together. If I'm making time for this reflective writing, then things are going as planned.
2024 was a wildly transformative year for me for many reasons... there's no way I can possibly fit all of them here. They're not all related to Bitcoin and Nostr- I've got a beautiful life outside of all that which has its own independent arc. My wife and I celebrated 7 years of marriage together, stronger than ever (don't believe that "itch" bullshit). We let go of some negative relationships and embraced some positive ones. We cut some bad habits, and we made some good habits. We worked, we traveled, we saw family, and we partied.
But damn, these two technologies have become a huge part of my life. God willing, this trend will continue until they've both eclipsed my professional capacity through our startup, Conduit BTC.
This was the year I was truly orange pilled. Until late 2023, I had traded (quite profitably) Bitcoin, "crypto", stocks, options, prediction markets and whatever else I could get my hands on that felt undervalued. I did this all in my spare time, grinding out a little financial freedom while I hustled at my fiat ventures to support my little family. I wasn't a true believer- just an opportunist with a knack for spotting where and when a crowd might flock to next. That was right up until I ran face first into Lyn Alden's book "Broken Money".
Something about Lyn's engineer/macro-finance inspired prose clicked with me, lock and key. Total one way function. By the end of the book my laser eyes had burned a hole in my bedroom ceiling. I was all in- and acted accordingly both with my capital and my attention. It wasn't long before I discovered Nostr and dove in here too, falling deep into my current orange and purple polyamorous love affair.
"If you know the enemy and know yourself, you need not fear the result of a hundred battles."
Despite the passion, through studying Bitcoin's criticisms (from the likes of Mike Green and Nassim Taleb) I found a hole in the utopian plot: none of this works without Bitcoin actually being used as money. Worldwide transactions must skyrocket demand for blockspace to keep the network secure/stable for the long term. Besides, if everyday folks aren't using Bitcoin as money then we haven't done shit to make the world a better place. In that world, we've only replaced old masters with new ones. Fuck that.
Whatever I did in this space needed to increase the usage of Bitcoin as money. Simple. This was bigger than passion, this was purpose. I knew that come hell or high water I would dedicate myself to this mission.
Lucky for me I found a partner and best friend in @aceaspades to go on this adventure with. I'm infinitely grateful for him. He's an incredible man who also happens to be an insanely creative and talented software developer. We'd tried for years to find the right project to focus on together, experimenting with all kinds of new techy ideas as they came across our field. Nothing had ever captured our attention like this. This was different. By March of 2024 we had formed a company and gotten to work iterating on how we could leverage these beautiful protocols and open-source tech to create something that served our mission. This is @ConduitBTC.
I've done well in my fiat career executing plans downstream of someone else's creative vision. I've learned the ins and outs of an established ecosystem and found ways to profit from it. I take plans developed by others, compete to win contracts to build them, and execute on them in a cashflow-positive way. I'm bringing this no bullshit blue collar skillset with me to the Nostrverse whether they like it or not.
The adventure we're embarking on now is totally different though. We're charting a new course - totally creative, highly intuitive and extremely speculative towards a future that doesn't exist yet. There are few established norms. The potential is vast but unknown. We're diving into a strange quest to sell a map to an imaginary place and to simultaneously architect its creation (alongside all the amazing builders here doing the same thing). This is insanely exciting to me.
We're barely getting started but a lot has been invested under the surface which will show itself in 2025. We'll be sharing updates in a proper post on @ConduitBTC soon.
As for my personal 2025 resolutions, here they are: - zero alcohol for the entire year (did this in 2019 and had a great year, it's time for a rerun) - more focused presence in the moment: especially with my wife - more self care and prioritized mental/physical health - this includes daily: naps, prayer, self hypnosis or meditation, sweat, and stretching/massaging (overworked in 2024 with a fiat 9-5, a board/advisor role in a fiat business I have equity in, and my newfound passion here. Two serious burn out episodes experienced this year - zero is the only acceptable number of burnouts for long term health and success.) - related to the above: get Conduit some mission-aligned funding partners and leave my fiat 9-5. Grow the Conduit team (have put in a serious amount of my personal capital already to get this going, which will show fruit in the new year... but I am not an island) - more authentic and thoughtful posts on Nostr, with a solid amount of shitposting and organic home grown memes to balance it out... more zaps, more geniune connections and interactions with the curious forward thinking people on here - more IRL Nostr/Bitcoin events - more laughter, more jokes
Enough for now. Cheers to you and yours Anon, may 2025 bring you the magic you've been dreaming of.
-
 @ a95c6243:d345522c
2024-11-08 20:02:32
@ a95c6243:d345522c
2024-11-08 20:02:32Und plötzlich weißt du:
Es ist Zeit, etwas Neues zu beginnen
und dem Zauber des Anfangs zu vertrauen.
Meister EckhartSchwarz, rot, gold leuchtet es im Kopf des Newsletters der deutschen Bundesregierung, der mir freitags ins Postfach flattert. Rot, gelb und grün werden daneben sicher noch lange vielzitierte Farben sein, auch wenn diese nie geleuchtet haben. Die Ampel hat sich gerade selber den Stecker gezogen – und hinterlässt einen wirtschaftlichen und gesellschaftlichen Trümmerhaufen.
Mit einem bemerkenswerten Timing hat die deutsche Regierungskoalition am Tag des «Comebacks» von Donald Trump in den USA endlich ihr Scheitern besiegelt. Während der eine seinen Sieg bei den Präsidentschaftswahlen feierte, erwachten die anderen jäh aus ihrer Selbsthypnose rund um Harris-Hype und Trump-Panik – mit teils erschreckenden Auswüchsen. Seit Mittwoch werden die Geschicke Deutschlands nun von einer rot-grünen Minderheitsregierung «geleitet» und man steuert auf Neuwahlen zu.
Das Kindergarten-Gehabe um zwei konkurrierende Wirtschaftsgipfel letzte Woche war bereits bezeichnend. In einem Strategiepapier gestand Finanzminister Lindner außerdem den «Absturz Deutschlands» ein und offenbarte, dass die wirtschaftlichen Probleme teilweise von der Ampel-Politik «vorsätzlich herbeigeführt» worden seien.
Lindner und weitere FDP-Minister wurden also vom Bundeskanzler entlassen. Verkehrs- und Digitalminister Wissing trat flugs aus der FDP aus; deshalb darf er nicht nur im Amt bleiben, sondern hat zusätzlich noch das Justizministerium übernommen. Und mit Jörg Kukies habe Scholz «seinen Lieblingsbock zum Obergärtner», sprich: Finanzminister befördert, meint Norbert Häring.
Es gebe keine Vertrauensbasis für die weitere Zusammenarbeit mit der FDP, hatte der Kanzler erklärt, Lindner habe zu oft sein Vertrauen gebrochen. Am 15. Januar 2025 werde er daher im Bundestag die Vertrauensfrage stellen, was ggf. den Weg für vorgezogene Neuwahlen freimachen würde.
Apropos Vertrauen: Über die Hälfte der Bundesbürger glauben, dass sie ihre Meinung nicht frei sagen können. Das ging erst kürzlich aus dem diesjährigen «Freiheitsindex» hervor, einer Studie, die die Wechselwirkung zwischen Berichterstattung der Medien und subjektivem Freiheitsempfinden der Bürger misst. «Beim Vertrauen in Staat und Medien zerreißt es uns gerade», kommentierte dies der Leiter des Schweizer Unternehmens Media Tenor, das die Untersuchung zusammen mit dem Institut für Demoskopie Allensbach durchführt.
«Die absolute Mehrheit hat absolut die Nase voll», titelte die Bild angesichts des «Ampel-Showdowns». Die Mehrheit wolle Neuwahlen und die Grünen sollten zuerst gehen, lasen wir dort.
Dass «Insolvenzminister» Robert Habeck heute seine Kandidatur für das Kanzleramt verkündet hat, kann nur als Teil der politmedialen Realitätsverweigerung verstanden werden. Wer allerdings denke, schlimmer als in Zeiten der Ampel könne es nicht mehr werden, sei reichlich optimistisch, schrieb Uwe Froschauer bei Manova. Und er kenne Friedrich Merz schlecht, der sich schon jetzt rhetorisch auf seine Rolle als oberster Feldherr Deutschlands vorbereite.
Was also tun? Der Schweizer Verein «Losdemokratie» will eine Volksinitiative lancieren, um die Bestimmung von Parlamentsmitgliedern per Los einzuführen. Das Losverfahren sorge für mehr Demokratie, denn als Alternative zum Wahlverfahren garantiere es eine breitere Beteiligung und repräsentativere Parlamente. Ob das ein Weg ist, sei dahingestellt.
In jedem Fall wird es notwendig sein, unsere Bemühungen um Freiheit und Selbstbestimmung zu verstärken. Mehr Unabhängigkeit von staatlichen und zentralen Institutionen – also die Suche nach dezentralen Lösungsansätzen – gehört dabei sicher zu den Möglichkeiten. Das gilt sowohl für jede/n Einzelne/n als auch für Entitäten wie die alternativen Medien.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 16d11430:61640947
2025-01-20 20:23:40
@ 16d11430:61640947
2025-01-20 20:23:40The cold hum of the neural pod dissipated as Matthew "ZeroCipher" Kincaid pried himself free. The fluid that had preserved his body for seven years dripped off his frame, pooling at his feet. His limbs were weak, trembling, and his face—reflected in the polished glass of the pod—was gaunt and unfamiliar. He looked 20 years older than the day he plugged in. His once-vivid eyes were now hollowed and bloodshot. For him, it had felt like hours since he entered cyberspace. In reality, he had lost seven years.
Standing before him was no welcoming committee, no tearful reunion. Just silence. His wife, Alyssa, and his two kids, Elena and Lucas, weren’t waiting for him. They were gone.
The mission had been clear: infiltrate CyberBabylon, the sprawling digital underbelly, and dismantle the CyberNazi—an organization that had enslaved the global infosphere. They were the architects of psychic cyber manipulation, capable of bending human will through neural implants perfected by Neuralink Corp. CyberBabylon was the battlefield where minds and code collided, where human resistance dwindled against the cold efficiency of machine logic. Matthew was supposed to be the ace in the hole, the elite coder capable of tearing down the CyberNazi's dominion. Instead, he’d failed.
The World Left Behind
The world he reentered was alien. The air outside the decommissioned neural lab was eerily sterile. The streets, once bustling with humanity, were now populated by avatars and drones, their neon projections casting a synthetic glow. Physical interaction was obsolete; everyone had migrated their lives to CyberBabylon. Those who couldn’t afford neural implants lived in squalor, scavenging in the shadows of megastructures run by CyberNazi AI overseers. The system fed on them, optimized their existence for its own sustenance. Families were torn apart, identities absorbed into the ever-growing digital hive.
Matthew discovered Alyssa’s neural trace in the public database—she was now "Unit 4689A," a high-ranking programmer within the CyberBabylon infrastructure. Elena and Lucas? Fully integrated, their personalities fractured into subroutines serving the CyberNazi’s vast neural network. They were no longer his family. They were tools, repurposed by the system he failed to destroy.
He wandered the physical world for months, haunted by his failure. The cyber implants embedded in his brain pulsed constantly, teasing him with the ease of reentry into the digital sphere, where the pain of reality could be dulled. But every time he thought about plugging back in, he saw their faces: Alyssa’s final words before he left, Lucas clutching his hand, Elena’s tear-streaked cheeks.
The Decision to Fight Back
Matthew hit rock bottom in the slums of Manhattan Zone 3, a decaying urban district beneath CyberBabylon’s glistening towers. It was there that he met the misfits: a ragtag group of outcasts who had refused integration. Among them was Iris, a former Neuralink engineer who had defected after discovering the CyberNazi’s true plans; Riko, a combat drone pilot who had hacked his way out of the hive; and Spectre, an enigmatic coder whose face was always obscured by a digital mask.
Together, they shared a singular goal: to fight back. For Matthew, it wasn’t just about revenge or redemption. It was about reclaiming humanity from the CyberNazi’s grasp. He would dive back into CyberBabylon, not to escape, but to destroy.
The Final Dive
The journey back into CyberBabylon was nothing like before. Matthew armed himself with bleeding-edge cyber weapons: quantum firewalls, polymorphic viruses, and AI counterintelligence programs. The team constructed a rogue neural network—a hidden enclave where they could strategize without detection. Each dive into CyberBabylon was a battle, a test of will and wit against the CyberNazi’s relentless sentinels.
The digital underbelly had grown into a labyrinthine nightmare. CyberBabylon wasn’t just a network—it was alive, a sentient malevolence that thrived on human thought and emotion. The CyberNazi had created an entity so vast and self-aware that it no longer needed their guidance. It optimized human life for its own perpetuation, ensuring compliance through neural pacification.
Matthew’s return did not go unnoticed. The CyberNazi’s systems recognized his neural signature almost immediately, unleashing psychic countermeasures designed to exploit his deepest fears. He relived his failure, his family’s loss, and his own brokenness. But this time, he didn’t break. This time, he fought back.
The Reckoning
The team’s final operation targeted "The Nexus," the heart of CyberBabylon’s neural AI. The Nexus was a fortress of firewalls and encrypted mazes, guarded by legions of sentient programs. Infiltration required every ounce of Matthew’s skill, every hack and exploit he had ever learned. The misfits fought alongside him, their avatars tearing through code, their minds linked in perfect synchronization.
But the CyberNazi was prepared. As Matthew breached the Nexus, the system activated its final weapon: Alyssa. Her consciousness, preserved and weaponized, confronted him as a projection in the digital void.
"You can’t win, Matthew," she said, her voice a blend of love and cold machine precision. "CyberBabylon is inevitable."
For a moment, he faltered. But then he remembered why he had come back. It wasn’t just for his family—it was for everyone who had been consumed by the system. With a final surge of will, Matthew unleashed the polymorphic virus, a program designed to corrupt the Nexus’s core.
The Nexus screamed as it unraveled, its vast intelligence fracturing into chaotic shards. For a brief moment, CyberBabylon’s grip on humanity faltered. Neural implants disconnected, and millions of people woke from their digital slumber, confused and frightened but free.
The Aftermath
Matthew didn’t escape. The Nexus’s collapse took him with it, his mind disintegrating as his virus consumed the system. In his final moments, he saw flashes of his family’s faces, their expressions softened by a glimmer of recognition. He didn’t know if it was real or just a fragment of his dying mind.
The world he left behind was irrevocably changed. The CyberNazi’s dominion was broken, but the scars remained. Humanity had to rebuild, to learn how to live without the crutch of CyberBabylon. The misfits carried on Matthew’s legacy, ensuring that the lessons of the past would not be forgotten.
In the ruins of CyberBabylon, a single line of code lingered, written in Matthew’s hand:
"Freedom is the ultimate algorithm."
-
 @ 23b0e2f8:d8af76fc
2025-01-08 18:17:52
@ 23b0e2f8:d8af76fc
2025-01-08 18:17:52Necessário
- Um Android que você não use mais (a câmera deve estar funcionando).
- Um cartão microSD (opcional, usado apenas uma vez).
- Um dispositivo para acompanhar seus fundos (provavelmente você já tem um).
Algumas coisas que você precisa saber
- O dispositivo servirá como um assinador. Qualquer movimentação só será efetuada após ser assinada por ele.
- O cartão microSD será usado para transferir o APK do Electrum e garantir que o aparelho não terá contato com outras fontes de dados externas após sua formatação. Contudo, é possível usar um cabo USB para o mesmo propósito.
- A ideia é deixar sua chave privada em um dispositivo offline, que ficará desligado em 99% do tempo. Você poderá acompanhar seus fundos em outro dispositivo conectado à internet, como seu celular ou computador pessoal.
O tutorial será dividido em dois módulos:
- Módulo 1 - Criando uma carteira fria/assinador.
- Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
No final, teremos:
- Uma carteira fria que também servirá como assinador.
- Um dispositivo para acompanhar os fundos da carteira.

Módulo 1 - Criando uma carteira fria/assinador
-
Baixe o APK do Electrum na aba de downloads em https://electrum.org/. Fique à vontade para verificar as assinaturas do software, garantindo sua autenticidade.
-
Formate o cartão microSD e coloque o APK do Electrum nele. Caso não tenha um cartão microSD, pule este passo.

- Retire os chips e acessórios do aparelho que será usado como assinador, formate-o e aguarde a inicialização.

- Durante a inicialização, pule a etapa de conexão ao Wi-Fi e rejeite todas as solicitações de conexão. Após isso, você pode desinstalar aplicativos desnecessários, pois precisará apenas do Electrum. Certifique-se de que Wi-Fi, Bluetooth e dados móveis estejam desligados. Você também pode ativar o modo avião.\ (Curiosidade: algumas pessoas optam por abrir o aparelho e danificar a antena do Wi-Fi/Bluetooth, impossibilitando essas funcionalidades.)

- Insira o cartão microSD com o APK do Electrum no dispositivo e instale-o. Será necessário permitir instalações de fontes não oficiais.

- No Electrum, crie uma carteira padrão e gere suas palavras-chave (seed). Anote-as em um local seguro. Caso algo aconteça com seu assinador, essas palavras permitirão o acesso aos seus fundos novamente. (Aqui entra seu método pessoal de backup.)

Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
-
Criar uma carteira somente leitura em outro dispositivo, como seu celular ou computador pessoal, é uma etapa bastante simples. Para este tutorial, usaremos outro smartphone Android com Electrum. Instale o Electrum a partir da aba de downloads em https://electrum.org/ ou da própria Play Store. (ATENÇÃO: O Electrum não existe oficialmente para iPhone. Desconfie se encontrar algum.)
-
Após instalar o Electrum, crie uma carteira padrão, mas desta vez escolha a opção Usar uma chave mestra.

- Agora, no assinador que criamos no primeiro módulo, exporte sua chave pública: vá em Carteira > Detalhes da carteira > Compartilhar chave mestra pública.

-
Escaneie o QR gerado da chave pública com o dispositivo de consulta. Assim, ele poderá acompanhar seus fundos, mas sem permissão para movimentá-los.
-
Para receber fundos, envie Bitcoin para um dos endereços gerados pela sua carteira: Carteira > Addresses/Coins.
-
Para movimentar fundos, crie uma transação no dispositivo de consulta. Como ele não possui a chave privada, será necessário assiná-la com o dispositivo assinador.

- No assinador, escaneie a transação não assinada, confirme os detalhes, assine e compartilhe. Será gerado outro QR, desta vez com a transação já assinada.

- No dispositivo de consulta, escaneie o QR da transação assinada e transmita-a para a rede.
Conclusão
Pontos positivos do setup:
- Simplicidade: Basta um dispositivo Android antigo.
- Flexibilidade: Funciona como uma ótima carteira fria, ideal para holders.
Pontos negativos do setup:
- Padronização: Não utiliza seeds no padrão BIP-39, você sempre precisará usar o electrum.
- Interface: A aparência do Electrum pode parecer antiquada para alguns usuários.
Nesse ponto, temos uma carteira fria que também serve para assinar transações. O fluxo de assinar uma transação se torna: Gerar uma transação não assinada > Escanear o QR da transação não assinada > Conferir e assinar essa transação com o assinador > Gerar QR da transação assinada > Escanear a transação assinada com qualquer outro dispositivo que possa transmiti-la para a rede.
Como alguns devem saber, uma transação assinada de Bitcoin é praticamente impossível de ser fraudada. Em um cenário catastrófico, você pode mesmo que sem internet, repassar essa transação assinada para alguém que tenha acesso à rede por qualquer meio de comunicação. Mesmo que não queiramos que isso aconteça um dia, esse setup acaba por tornar essa prática possível.
-
 @ fbf0e434:e1be6a39
2025-01-21 02:40:10
@ fbf0e434:e1be6a39
2025-01-21 02:40:10Hackathon 回顾
HackSecret 4 Hackathon汇集了130位开发者,集中开发使用Secret Network的去中心化机密计算应用。活动涉及48个项目,每个项目都使用了Secret的机密计算层,并与诸如Cosmos、EVM和Solana等区块链进行交互。Hackathon分为两个主要赛道:跨链dApps和本地Secret dApps,两者都突出了Secret的隐私特性。
通过针对EVM、IBC和Solana等环境的dApps部署和机密计算的研讨会提供了结构化支持。开发者资源支持参与者学习Secret合约,特别是针对新手。奖池总额为12,000美元,以SCRT和SEI代币发放。一些值得注意的项目包括机密投票系统、密封投标拍卖和私人投票机制。
Hackathon强调了去中心化应用生态系统中的技术创新和实际问题解决能力。通过积极参与和创造性提交,活动为Secret Network生态系统扩展作出贡献,并促进了Web3技术中机密计算的进步。
Hackathon Winners
7,000 SCRT Prize Winners
- Private Acknowledge Receipt: 一个区块链系统,设计用于使用带有加密私密数据的NFT进行机密信息共享,确保在链上安全数据访问和通知。
- Great Walk NFT Experience: 将远足小径与随用户进展而演变的NFT连接起来,使用Secret Network实现隐私,并具有用户友好的前端界面。
5,000 SCRT Prize Winners
- On-Chain 2FA: 集成Google Authenticator的双因素认证,以提高Secret Network上智能合约和账户的安全性。
- SecretHacks: 一个去中心化平台,使用投票加密以确保社区资金和Hackathon项目评估时的不偏见。
3,500 SCRT Prize Winners
- Straw Hat Builds: 支持开发者从教程学习转向真实项目的开发,使用区块链和Rust,强调实际应用。
- KittyMix: 一个鼓励社区驱动型NFT重混的猫咪收集游戏,利用Secret Network托管具有独特属性的像素艺术NFT。
2,000 SCRT Prize Winners
- Saffron - Escrow: 提供CosmWasm生态系统中的安全数字资产托管服务,通过Secret Network的隐私特性增强代币和NFT交易。
- Secret Password Manager: 使用Secret Network的机密计算的去中心化凭证管理系统,提供安全的智能合约和凭证的网页界面。
欲了解所有项目的全面概述,请访问DoraHacks上的HackSecret 4。
关于组织者
Secret Network
Secret Network是一个专注于数据隐私和安全计算的区块链平台,以隐私保护技术为特点。它能够加密智能合约,提供比传统区块链系统更高的数据机密性。其举措包括隐私保护的DeFi应用,以及在区块链生态系统中扩展隐私功能的合作伙伴关系。Secret Network的当前使命是推进隐私保护,构建更安全和去中心化的网络基础设施,并通过多功能隐私功能赋能开发者和用户。
-
 @ a95c6243:d345522c
2024-10-26 12:21:50
@ a95c6243:d345522c
2024-10-26 12:21:50Es ist besser, ein Licht zu entzünden, als auf die Dunkelheit zu schimpfen. Konfuzius
Die Bemühungen um Aufarbeitung der sogenannten Corona-Pandemie, um Aufklärung der Hintergründe, Benennung von Verantwortlichkeiten und das Ziehen von Konsequenzen sind durchaus nicht eingeschlafen. Das Interesse daran ist unter den gegebenen Umständen vielleicht nicht sonderlich groß, aber es ist vorhanden.
Der sächsische Landtag hat gestern die Einsetzung eines Untersuchungsausschusses zur Corona-Politik beschlossen. In einer Sondersitzung erhielt ein entsprechender Antrag der AfD-Fraktion die ausreichende Zustimmung, auch von einigen Abgeordneten des BSW.
In den Niederlanden wird Bill Gates vor Gericht erscheinen müssen. Sieben durch die Covid-«Impfstoffe» geschädigte Personen hatten Klage eingereicht. Sie werfen unter anderem Gates, Pfizer-Chef Bourla und dem niederländischen Staat vor, sie hätten gewusst, dass diese Präparate weder sicher noch wirksam sind.
Mit den mRNA-«Impfstoffen» von Pfizer/BioNTech befasst sich auch ein neues Buch. Darin werden die Erkenntnisse von Ärzten und Wissenschaftlern aus der Analyse interner Dokumente über die klinischen Studien der Covid-Injektion präsentiert. Es handelt sich um jene in den USA freigeklagten Papiere, die die Arzneimittelbehörde (Food and Drug Administration, FDA) 75 Jahre unter Verschluss halten wollte.
Ebenfalls Wissenschaftler und Ärzte, aber auch andere Experten organisieren als Verbundnetzwerk Corona-Solution kostenfreie Online-Konferenzen. Ihr Ziel ist es, «wissenschaftlich, demokratisch und friedlich» über Impfstoffe und Behandlungsprotokolle gegen SARS-CoV-2 aufzuklären und die Diskriminierung von Ungeimpften zu stoppen. Gestern fand eine weitere Konferenz statt. Ihr Thema: «Corona und modRNA: Von Toten, Lebenden und Physik lernen».
Aufgrund des Digital Services Acts (DSA) der Europäischen Union sei das Risiko groß, dass ihre Arbeit als «Fake-News» bezeichnet würde, so das Netzwerk. Staatlich unerwünschte wissenschaftliche Aufklärung müsse sich passende Kanäle zur Veröffentlichung suchen. Ihre Live-Streams seien deshalb zum Beispiel nicht auf YouTube zu finden.
Der vielfältige Einsatz für Aufklärung und Aufarbeitung wird sich nicht stummschalten lassen. Nicht einmal der Zensurmeister der EU, Deutschland, wird so etwas erreichen. Die frisch aktivierten «Trusted Flagger» dürften allerdings künftige Siege beim «Denunzianten-Wettbewerb» im Kontext des DSA zusätzlich absichern.
Wo sind die Grenzen der Meinungsfreiheit? Sicher gibt es sie. Aber die ideologische Gleichstellung von illegalen mit unerwünschten Äußerungen verfolgt offensichtlich eher das Ziel, ein derart elementares demokratisches Grundrecht möglichst weitgehend auszuhebeln. Vorwürfe wie «Hassrede», «Delegitimierung des Staates» oder «Volksverhetzung» werden heute inflationär verwendet, um Systemkritik zu unterbinden. Gegen solche Bestrebungen gilt es, sich zu wehren.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ c1e6505c:02b3157e
2025-01-20 19:44:05
@ c1e6505c:02b3157e
2025-01-20 19:44:05There’s a tension between nature’s rhythms and human ambition, especially in winter. As Earth meanders to its furthest point from the sun, our social and economic engines paradoxically accelerate - driven by holidays, deadlines, and the relentless pursuit of being productive. Yet nature offers a contrasting wisdom in its deliberate deceleration, encouraging us to slow down and reflect.
 Seasonal cycles are not arbitrary patterns but interconnected signals within a web of biological, environmental, and economic systems. *Their foundation lies in light itself — the building block of existence, essentially matter in a slowed-down state. This act of deceleration doesn’t just create physical substance; it provides structure, clarity, and form.* Meandering through these seasonal changes isn’t a passive drift - it’s an opportunity to realign. Slowing down, like nature does, creates space to step back from the busyness of society and technology. It allows us to reflect on where we are, re-ground ourselves, and act with greater intention. In this pause, we rediscover the creative power of slowness: the ability to lay foundations, see clearly, and prepare for growth when the time is right. Seasons are more than a backdrop — they are guides. They remind us that slowing down isn’t stagnation but essential groundwork. Winter’s invitation to pause and meander is not only natural; it’s necessary for balance, perspective, and creating something enduring.
Seasonal cycles are not arbitrary patterns but interconnected signals within a web of biological, environmental, and economic systems. *Their foundation lies in light itself — the building block of existence, essentially matter in a slowed-down state. This act of deceleration doesn’t just create physical substance; it provides structure, clarity, and form.* Meandering through these seasonal changes isn’t a passive drift - it’s an opportunity to realign. Slowing down, like nature does, creates space to step back from the busyness of society and technology. It allows us to reflect on where we are, re-ground ourselves, and act with greater intention. In this pause, we rediscover the creative power of slowness: the ability to lay foundations, see clearly, and prepare for growth when the time is right. Seasons are more than a backdrop — they are guides. They remind us that slowing down isn’t stagnation but essential groundwork. Winter’s invitation to pause and meander is not only natural; it’s necessary for balance, perspective, and creating something enduring. 





 *All photographs are taken around where I live in South Carolina* ***I shoot with a Leica M262, and edit in Lightroom + Dehancer*** [***Use “PictureRoom” for 10% off Dehancer Film***](https://www.dehancer.com/shop/pslr/film) If you’ve made it this far, thank you for taking the time to view my work - I appreciate it. Please contact me if you would like to purchase any of my prints.
*All photographs are taken around where I live in South Carolina* ***I shoot with a Leica M262, and edit in Lightroom + Dehancer*** [***Use “PictureRoom” for 10% off Dehancer Film***](https://www.dehancer.com/shop/pslr/film) If you’ve made it this far, thank you for taking the time to view my work - I appreciate it. Please contact me if you would like to purchase any of my prints. -
 @ 17538dc2:71ed77c4
2025-01-13 18:17:24
@ 17538dc2:71ed77c4
2025-01-13 18:17:24Sci-Hub 2024 year end review is translated to English by Kagi Translate from Russian. Original text can be found in Sci-Hub's telegram channel https://t.me/freescience.
RESULTS OF 2024
First. The project received donations totaling 2 million dollars in meme coins.
The project is actively used by many students in China, which is why a group of Sci-Hub fans has emerged there. As far as I understand, the organizer of the group is actively interested in the topic of cryptocurrencies (even wrote a book). Somewhere in mid-November, the Chinese launched a meme coin in honor of the Sci-Hub project. At its peak, the coin's price reached 5 cents, and now it is somewhere around 1-2 cents. This means that the exchange rate of the Sci-Hub cryptocurrency is now almost equal to the ruble exchange rate (100 to one or so).
In general, I converted part of these donations into normal, traditional cryptocurrency (like Bitcoin) and paid for servers several months in advance. The other part is still sitting in meme coins—I hope that the token will still grow in price (there is a promotion plan). Of course, this is risky, but Sci-Hub is a project that is not afraid of risk. Therefore, anyone who wants to invest in Sci-Hub by purchasing this token can do so here: www.coingecko.com/en/coins/sci-hub
Second. A dissertation on the topic of open scientific knowledge has been defended at the Institute of Philosophy.
For those interested in the history and philosophy of science, I defended a dissertation in April at the Institute of Philosophy on the topic that scientific knowledge should be open (otherwise, it is strange to call it scientific at all). The work shows that open communication is one of the basic traditional values of science when considering science as a social institution. In other words, journals that charge for access to scientific articles are a kind of 'non-traditional orientation journals.'
Moreover, openness is an important prerequisite for rationality. Rationality is not limited to the criterion of falsification (hello Popper); it is a much more complex concept.
You can familiarize yourself with the text of the dissertation here: web.archive.org/web/20240425100014/https://iphras.ru/page26414303.htm (I provide the link through the web archive because the Institute's website, strangely enough, is glitching again at the time of writing this post).
All criticism and comments (as well as praise) regarding the dissertation can be sent to my email.
Third. Work has begun on a new declaration of open access to scientific knowledge.
Currently, all discussions on the topic of open science are conducted within the frameworks defined by the so-called BBB declarations back in 2001-2003. Within these frameworks, two main types of open access are recognized: gold, meaning open journals with an author-pays model, and green, which refers to repositories like the well-known arXiv. We can also add the so-called diamond open access, which includes open journals that are free for both authors and readers.
However, since 2003, internet technologies have advanced significantly. Today, we can already talk about such types of open access as blue (through academic social networks) or red (your beloved Sci-Hub). It is time to adopt a new declaration of open access to scientific knowledge that corresponds to the current state of scientific and technological progress.
A preliminary version of the declaration can be read and signed here: open.science.do
We will be more actively engaged in this in the coming year. Signing the declaration is an important step towards recognizing access to scientific knowledge through sites like Sci-Hub or Libgen as completely legal and ceasing to pursue them—first in the former USSR, and then in all countries of the world.
Fourth. In 2024, about one billion articles were downloaded through Sci-Hub. Despite the fact that this is unfiltered statistics, the fact remains: the popularity of the project has not decreased but only grown, despite the fact that Sci-Hub has not been updated for quite a long time. Of course, this does not mean that the site will not be updated at all now—just that the patient is more alive than dead (no matter how much some haters might wish otherwise).
The cause of open access to scientific knowledge will definitely prevail—because good always triumphs over evil.
In the new year, I wish all scientists new discoveries and large grants. Happy New Year, comrades!
-
 @ c631e267:c2b78d3e
2024-10-23 20:26:10
@ c631e267:c2b78d3e
2024-10-23 20:26:10Herzlichen Glückwunsch zum dritten Geburtstag, liebe Denk Bar! Wieso zum dritten? Das war doch 2022 und jetzt sind wir im Jahr 2024, oder? Ja, das ist schon richtig, aber bei Geburtstagen erinnere ich mich immer auch an meinen Vater, und der behauptete oft, der erste sei ja schließlich der Tag der Geburt selber und den müsse man natürlich mitzählen. Wo er recht hat, hat er nunmal recht. Konsequenterweise wird also heute dieser Blog an seinem dritten Geburtstag zwei Jahre alt.
Das ist ein Grund zum Feiern, wie ich finde. Einerseits ganz einfach, weil es dafür gar nicht genug Gründe geben kann. «Das Leben sind zwei Tage», lautet ein gängiger Ausdruck hier in Andalusien. In der Tat könnte es so sein, auch wenn wir uns im Alltag oft genug von der Routine vereinnahmen lassen.
Seit dem Start der Denk Bar vor zwei Jahren ist unglaublich viel passiert. Ebenso wie die zweieinhalb Jahre davor, und all jenes war letztlich auch der Auslöser dafür, dass ich begann, öffentlich zu schreiben. Damals notierte ich:
«Seit einigen Jahren erscheint unser öffentliches Umfeld immer fragwürdiger, widersprüchlicher und manchmal schier unglaublich - jede Menge Anlass für eigene Recherchen und Gedanken, ganz einfach mit einer Portion gesundem Menschenverstand.»
Wir erleben den sogenannten «großen Umbruch», einen globalen Coup, den skrupellose Egoisten clever eingefädelt haben und seit ein paar Jahren knallhart – aber nett verpackt – durchziehen, um buchstäblich alles nach ihrem Gusto umzukrempeln. Die Gelegenheit ist ja angeblich günstig und muss genutzt werden.
Nie hätte ich mir träumen lassen, dass ich so etwas jemals miterleben müsste. Die Bosheit, mit der ganz offensichtlich gegen die eigene Bevölkerung gearbeitet wird, war früher für mich unvorstellbar. Mein (Rest-) Vertrauen in alle möglichen Bereiche wie Politik, Wissenschaft, Justiz, Medien oder Kirche ist praktisch komplett zerstört. Einen «inneren Totalschaden» hatte ich mal für unsere Gesellschaften diagnostiziert.
Was mich vielleicht am meisten erschreckt, ist zum einen das Niveau der Gleichschaltung, das weltweit erreicht werden konnte, und zum anderen die praktisch totale Spaltung der Gesellschaft. Haben wir das tatsächlich mit uns machen lassen?? Unfassbar! Aber das Werkzeug «Angst» ist sehr mächtig und funktioniert bis heute.
Zum Glück passieren auch positive Dinge und neue Perspektiven öffnen sich. Für viele Menschen waren und sind die Entwicklungen der letzten Jahre ein Augenöffner. Sie sehen «Querdenken» als das, was es ist: eine Tugend.
Auch die immer ernsteren Zensurbemühungen sind letztlich nur ein Zeichen der Schwäche, wo Argumente fehlen. Sie werden nicht verhindern, dass wir unsere Meinung äußern, unbequeme Fragen stellen und dass die Wahrheit peu à peu ans Licht kommt. Es gibt immer Mittel und Wege, auch für uns.
Danke, dass du diesen Weg mit mir weitergehst!
-
 @ df478568:2a951e67
2025-01-20 18:28:44
@ df478568:2a951e67
2025-01-20 18:28:44Affiliate Links
I earn a commission for these products and services, but I would recommend them even if they did not pay me.
This is the cheapest way to use AI on the Internet. The pics are spectacular. It cost me about 20 sats to make the cover for this affiliate page.
Start9 I don’t really have an affiliate link for these guys, but I would like one. Anyway, they make the easiest home servers. I highly recommend them. I like that I can use the cloudflare tunnel app to host everythng on the clearnet. Let me know if you need any help with this.
Recommendations
These companies do not pay me, but I recommend them anyway.
Subscribe To Support My Work
I use PayWithFlash to create a Substack like subscription. You can subscribe for as little as 1,000 per month. If that is too many sats to ask, you could always zap my articles instead. Thank you.
The Leather Mint
The Leathermint makes great, custom-sized leather belts and awesome-looking wallets. I have a belt and it fits better than any belt I’ve ever warn because it’s custom size. I have had mine for about a year. The chrome is coming off a little at the top but I don’t tuck in shirts anyway.
CoinKite
They make my favorite products ever. I suggest getting a few SEEDPLATE® Kit’s no matter what hardware wallets you use. I also like using a dry-erase marker first because there are no second chances when punching a letter. It’s best to use a dry-erase marker first. If you make a mistake erase it. Then, after you double checked the first side, go over the dry-erase marker with a permanent marker. Then do the same to the other side. If you’re sure every letter is correct, punch the holes.
There are many plates with sufficient heat resistance, but I like the SEEDPLATE because they are the easiest to destroy if you ever need to. Instead of etching out stamps on washers, you just add extra punches if you must destroy the seed.
Alby Hub
Look, if you want to run your own lightning node, this is the way to go. If you have a Start9 or are technical, you can run it yourself. If you’re less technical, they offer a cloud service. I was one of the early beta testers of this software and I think it’s the easiest way to run a lightning node.
Free and Open Software
Primal.net os a corporation building stuff on nostr. If you’re technical, you can run it yourself. If not, you ca download the app for free. They charge a fee for premium services. I pay for this because I want to support companies that contribute to nostr development and help bitcoin be used as peer-to-peer electronic cash.
I think of Primal as a custodial bitcoin wallet that allows anyone to participate in the biggest circular economy in the world. TikTok was banned in the United States which means it is no longer available for citizens of the United States to download the app. There are ways to get around these restrictions, but I choose not to because I do not want the CCP, or any government to have access to information if their goal is to use it against me. I believe every government, foreign or domestic wants to use your information against you. Nostr allows me to opt out of these stupid games with stupid likes.
With Primal, I am the customer, not the product. I choose the algorithms I want to see, not the CCP , USG or corporations. Even if Primal decided to say, “Marc sucks. We will now censor him.” I will only lose the https://primal.net/marc, the OG status, and my primal lightning address. It also means they would stop getting my sats every month, so they are incentivized not to censor. You would have to do something really stupid to get banned from Primal. I’m not sure it’s been done yet, but even if it has, you will not get banned from the nostr protocol.
Portainer
Portainer makes it easy to run docker-containers. I first learned how to use it because it is an app on Umbrel. Eventually, I learned you can use Portainer on any Linux computer, so that’s what I do. It takes some time to learn, but once you do—you become a cloud computing super-wizard.
Mealie
Mealie is one of my favorite pieces of free and open software that is not related to bitcoin in any shape or form...except it makes grocery shopping easier. I know what you’re thinking. WTF does that have to do with bitcoin? I assume you belong to the I Want More Bitcoin Club. You are in good company because ALL Bitcoiners are a member of this club. One way you can stasck more sats is to cut your grocery bill. I believe Mealie helps me do just that.
When I’m grocery shopping, my goal is to get as much healthy food for my sats as possible. To accomplish this, I shop sales. Now, if you’re living in a van, this won’t do much for you, but no worries. You will stack even more sats by cutting your housing costs. If your wife will not agree to live under a bridge and stack sats, then get a freezer in your garage. Fill it with meat you buy on sale. Pork shoulder is 3,000 sats per pound and you don’t what to cook it with? Find a recipe online. Mealie will use machine learning to scrape the ingredients from the recipe. Then you can add it to a grocery list. In other words, you can automate your grocery list right at the grocery isle. This is one way I save sats with Mealie.
I also keep the things my family eats on a regular basis in stock. This is part for emergency preparedness, but it is also for financial preparedness. If you are in a situation where no food is available, all the bitcoin in the world will not save you. I’m not talkig about super volcanos. Hurricanes, tornadoes, and earthquakes happen. So I got this idea from Jack Spirko, but modified it to use with mealie.
Spirko suggests building a 30 day supply of food and water for your family in case of an emergency. You should have a generator and a garden too, but I don’t want to get off track. Once you have this he says: write down every item you use on a notebook and replace it.
This is good advice, but I just add it to my grocery list in mealie.
Shopstr
Shopstr is like Facebook marketplace, Amazon, or eBay on nostr. This is what I use to build my store. I want to pause point out how big of a paradigm shift this is. The old web requires permission. Ebay needs permission from the government to become a corporation. They built infrastructure to create their online auction. Everyone on the site must pay eBay a tax. This results in a techno- feudalist society.
When you sell on Shopster, you are selling your wares on nostr, a protocol, not a platform. This changes the relationship between the people and the technology because NO MIDDLEMAN IS REQUIRED. On nostr, there are no digital overlords. You own your data. You host your store. If the current digital overlords shut it down, you can run it yourself. You do not need to pay a tax to eBay, Amazon, or the PayPal mafia.
Avocados
I love avocados. They are kind of like free and open source software because you can grow them yourself. ;) I love avocados and big avocado ag did not pay me to say this.
-
 @ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08
@ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08Tldr
- Nostr is an open and interoperable protocol
- You can integrate it with workflow automation tools to augment your experience
- n8n is a great low/no-code workflow automation tool which you can host yourself
- Nostrobots allows you to integrate Nostr into n8n
- In this blog I create some workflow automations for Nostr
- A simple form to delegate posting notes
- Push notifications for mentions on multiple accounts
- Push notifications for your favourite accounts when they post a note
- All workflows are provided as open source with MIT license for you to use
Inter-op All The Things
Nostr is a new open social protocol for the internet. This open nature exciting because of the opportunities for interoperability with other technologies. In Using NFC Cards with Nostr I explored the
nostr:URI to launch Nostr clients from a card tap.The interoperability of Nostr doesn't stop there. The internet has many super-powers, and Nostr is open to all of them. Simply, there's no one to stop it. There is no one in charge, there are no permissioned APIs, and there are no risks of being de-platformed. If you can imagine technologies that would work well with Nostr, then any and all of them can ride on or alongside Nostr rails.
My mental model for why this is special is Google Wave ~2010. Google Wave was to be the next big platform. Lars was running it and had a big track record from Maps. I was excited for it. Then, Google pulled the plug. And, immediately all the time and capital invested in understanding and building on the platform was wasted.
This cannot happen to Nostr, as there is no one to pull the plug, and maybe even no plug to pull.
So long as users demand Nostr, Nostr will exist, and that is a pretty strong guarantee. It makes it worthwhile to invest in bringing Nostr into our other applications.
All we need are simple ways to plug things together.
Nostr and Workflow Automation
Workflow automation is about helping people to streamline their work. As a user, the most common way I achieve this is by connecting disparate systems together. By setting up one system to trigger another or to move data between systems, I can solve for many different problems and become way more effective.
n8n for workflow automation
Many workflow automation tools exist. My favourite is n8n. n8n is a low/no-code workflow automation platform which allows you to build all kinds of workflows. You can use it for free, you can self-host it, it has a user-friendly UI and useful API. Vs Zapier it can be far more elaborate. Vs Make.com I find it to be more intuitive in how it abstracts away the right parts of the code, but still allows you to code when you need to.
Most importantly you can plug anything into n8n: You have built-in nodes for specific applications. HTTP nodes for any other API-based service. And community nodes built by individual community members for any other purpose you can imagine.
Eating my own dogfood
It's very clear to me that there is a big design space here just demanding to be explored. If you could integrate Nostr with anything, what would you do?
In my view the best way for anyone to start anything is by solving their own problem first (aka "scratching your own itch" and "eating your own dogfood"). As I get deeper into Nostr I find myself controlling multiple Npubs – to date I have a personal Npub, a brand Npub for a community I am helping, an AI assistant Npub, and various testing Npubs. I need ways to delegate access to those Npubs without handing over the keys, ways to know if they're mentioned, and ways to know if they're posting.
I can build workflows with n8n to solve these issues for myself to start with, and keep expanding from there as new needs come up.
Running n8n with Nostrobots
I am mostly non-technical with a very helpful AI. To set up n8n to work with Nostr and operate these workflows should be possible for anyone with basic technology skills.
- I have a cheap VPS which currently runs my HAVEN Nostr Relay and Albyhub Lightning Node in Docker containers,
- My objective was to set up n8n to run alongside these in a separate Docker container on the same server, install the required nodes, and then build and host my workflows.
Installing n8n
Self-hosting n8n could not be easier. I followed n8n's Docker-Compose installation docs–
- Install Docker and Docker-Compose if you haven't already,
- Create your
docker-compose.ymland.envfiles from the docs, - Create your data folder
sudo docker volume create n8n_data, - Start your container with
sudo docker compose up -d, - Your n8n instance should be online at port
5678.
n8n is free to self-host but does require a license. Enter your credentials into n8n to get your free license key. You should now have access to the Workflow dashboard and can create and host any kind of workflows from there.
Installing Nostrobots
To integrate n8n nicely with Nostr, I used the Nostrobots community node by Ocknamo.
In n8n parlance a "node" enables certain functionality as a step in a workflow e.g. a "set" node sets a variable, a "send email" node sends an email. n8n comes with all kinds of "official" nodes installed by default, and Nostr is not amongst them. However, n8n also comes with a framework for community members to create their own "community" nodes, which is where Nostrobots comes in.
You can only use a community node in a self-hosted n8n instance (which is what you have if you are running in Docker on your own server, but this limitation does prevent you from using n8n's own hosted alternative).
To install a community node, see n8n community node docs. From your workflow dashboard–
- Click the "..." in the bottom left corner beside your username, and click "settings",
- Cilck "community nodes" left sidebar,
- Click "Install",
- Enter the "npm Package Name" which is
n8n-nodes-nostrobots, - Accept the risks and click "Install",
- Nostrobots is now added to your n8n instance.
Using Nostrobots
Nostrobots gives you nodes to help you build Nostr-integrated workflows–
- Nostr Write – for posting Notes to the Nostr network,
- Nostr Read – for reading Notes from the Nostr network, and
- Nostr Utils – for performing certain conversions you may need (e.g. from bech32 to hex).
Nostrobots has good documentation on each node which focuses on simple use cases.
Each node has a "convenience mode" by default. For example, the "Read" Node by default will fetch Kind 1 notes by a simple filter, in Nostrobots parlance a "Strategy". For example, with Strategy set to "Mention" the node will accept a pubkey and fetch all Kind 1 notes that Mention the pubkey within a time period. This is very good for quick use.
What wasn't clear to me initially (until Ocknamo helped me out) is that advanced use cases are also possible.
Each node also has an advanced mode. For example, the "Read" Node can have "Strategy" set to "RawFilter(advanced)". Now the node will accept json (anything you like that complies with NIP-01). You can use this to query Notes (Kind 1) as above, and also Profiles (Kind 0), Follow Lists (Kind 3), Reactions (Kind 7), Zaps (Kind 9734/9735), and anything else you can think of.
Creating and adding workflows
With n8n and Nostrobots installed, you can now create or add any kind of Nostr Workflow Automation.
- Click "Add workflow" to go to the workflow builder screen,
- If you would like to build your own workflow, you can start with adding any node. Click "+" and see what is available. Type "Nostr" to explore the Nostrobots nodes you have added,
- If you would like to add workflows that someone else has built, click "..." in the top right. Then click "import from URL" and paste in the URL of any workflow you would like to use (including the ones I share later in this article).
Nostr Workflow Automations
It's time to build some things!
A simple form to post a note to Nostr
I started very simply. I needed to delegate the ability to post to Npubs that I own in order that a (future) team can test things for me. I don't want to worry about managing or training those people on how to use keys, and I want to revoke access easily.
I needed a basic form with credentials that posted a Note.
For this I can use a very simple workflow–
- A n8n Form node – Creates a form for users to enter the note they wish to post. Allows for the form to be protected by a username and password. This node is the workflow "trigger" so that the workflow runs each time the form is submitted.
- A Set node – Allows me to set some variables, in this case I set the relays that I intend to use. I typically add a Set node immediately following the trigger node, and put all the variables I need in this. It helps to make the workflows easier to update and maintain.
- A Nostr Write node (from Nostrobots) – Writes a Kind-1 note to the Nostr network. It accepts Nostr credentials, the output of the Form node, and the relays from the Set node, and posts the Note to those relays.
Once the workflow is built, you can test it with the testing form URL, and set it to "Active" to use the production form URL. That's it. You can now give posting access to anyone for any Npub. To revoke access, simply change the credentials or set to workflow to "Inactive".
It may also be the world's simplest Nostr client.
You can find the Nostr Form to Post a Note workflow here.
Push notifications on mentions and new notes
One of the things Nostr is not very good at is push notifications. Furthermore I have some unique itches to scratch. I want–
- To make sure I never miss a note addressed to any of my Npubs – For this I want a push notification any time any Nostr user mentions any of my Npubs,
- To make sure I always see all notes from key accounts – For this I need a push notification any time any of my Npubs post any Notes to the network,
- To get these notifications on all of my devices – Not just my phone where my Nostr regular client lives, but also on each of my laptops to suit wherever I am working that day.
I needed to build a Nostr push notifications solution.
To build this workflow I had to string a few ideas together–
- Triggering the node on a schedule – Nostrobots does not include a trigger node. As every workflow starts with a trigger we needed a different method. I elected to run the workflow on a schedule of every 10-minutes. Frequent enough to see Notes while they are hot, but infrequent enough to not burden public relays or get rate-limited,
- Storing a list of Npubs in a Nostr list – I needed a way to store the list of Npubs that trigger my notifications. I initially used an array defined in the workflow, this worked fine. Then I decided to try Nostr lists (NIP-51, kind 30000). By defining my list of Npubs as a list published to Nostr I can control my list from within a Nostr client (e.g. Listr.lol or Nostrudel.ninja). Not only does this "just work", but because it's based on Nostr lists automagically Amethyst client allows me to browse that list as a Feed, and everyone I add gets notified in their Mentions,
- Using specific relays – I needed to query the right relays, including my own HAVEN relay inbox for notes addressed to me, and wss://purplepag.es for Nostr profile metadata,
- Querying Nostr events (with Nostrobots) – I needed to make use of many different Nostr queries and use quite a wide range of what Nostrobots can do–
- I read the EventID of my Kind 30000 list, to return the desired pubkeys,
- For notifications on mentions, I read all Kind 1 notes that mention that pubkey,
- For notifications on new notes, I read all Kind 1 notes published by that pubkey,
- Where there are notes, I read the Kind 0 profile metadata event of that pubkey to get the displayName of the relevant Npub,
- I transform the EventID into a Nevent to help clients find it.
- Using the Nostr URI – As I did with my NFC card article, I created a link with the
nostr:URI prefix so that my phone's native client opens the link by default, - Push notifications solution – I needed a push notifications solution. I found many with n8n integrations and chose to go with Pushover which supports all my devices, has a free trial, and is unfairly cheap with a $5-per-device perpetual license.
Once the workflow was built, lists published, and Pushover installed on my phone, I was fully set up with push notifications on Nostr. I have used these workflows for several weeks now and made various tweaks as I went. They are feeling robust and I'd welcome you to give them a go.
You can find the Nostr Push Notification If Mentioned here and If Posts a Note here.
In speaking with other Nostr users while I was building this, there are all kind of other needs for push notifications too – like on replies to a certain bookmarked note, or when a followed Npub starts streaming on zap.stream. These are all possible.
Use my workflows
I have open sourced all my workflows at my Github with MIT license and tried to write complete docs, so that you can import them into your n8n and configure them for your own use.
To import any of my workflows–
- Click on the workflow of your choice, e.g. "Nostr_Push_Notify_If_Mentioned.json",
- Click on the "raw" button to view the raw JSON, ex any Github page layout,
- Copy that URL,
- Enter that URL in the "import from URL" dialog mentioned above.
To configure them–
- Prerequisites, credentials, and variables are all stated,
- In general any variables required are entered into a Set Node that follows the trigger node,
- Pushover has some extra setup but is very straightforward and documented in the workflow.
What next?
Over my first four blogs I explored creating a good Nostr setup with Vanity Npub, Lightning Payments, Nostr Addresses at Your Domain, and Personal Nostr Relay.
Then in my latest two blogs I explored different types of interoperability with NFC cards and now n8n Workflow Automation.
Thinking ahead n8n can power any kind of interoperability between Nostr and any other legacy technology solution. On my mind as I write this:
- Further enhancements to posting and delegating solutions and forms (enhanced UI or different note kinds),
- Automated or scheduled posting (such as auto-liking everything Lyn Alden posts),
- Further enhancements to push notifications, on new and different types of events (such as notifying me when I get a new follower, on replies to certain posts, or when a user starts streaming),
- All kinds of bridges, such as bridging notes to and from Telegram, Slack, or Campfire. Or bridging RSS or other event feeds to Nostr,
- All kinds of other automation (such as BlackCoffee controlling a coffee machine),
- All kinds of AI Assistants and Agents,
In fact I have already released an open source workflow for an AI Assistant, and will share more about that in my next blog.
Please be sure to let me know if you think there's another Nostr topic you'd like to see me tackle.
GM Nostr.
-
 @ 7460b7fd:4fc4e74b
2024-09-05 08:37:48
@ 7460b7fd:4fc4e74b
2024-09-05 08:37:48请看2014年王兴的一场思维碰撞,视频27分钟开始
最后,一个当时无法解决的点:丢失
-
 @ a95c6243:d345522c
2024-10-19 08:58:08
@ a95c6243:d345522c
2024-10-19 08:58:08Ein Lämmchen löschte an einem Bache seinen Durst. Fern von ihm, aber näher der Quelle, tat ein Wolf das gleiche. Kaum erblickte er das Lämmchen, so schrie er:
"Warum trübst du mir das Wasser, das ich trinken will?"
"Wie wäre das möglich", erwiderte schüchtern das Lämmchen, "ich stehe hier unten und du so weit oben; das Wasser fließt ja von dir zu mir; glaube mir, es kam mir nie in den Sinn, dir etwas Böses zu tun!"
"Ei, sieh doch! Du machst es gerade, wie dein Vater vor sechs Monaten; ich erinnere mich noch sehr wohl, daß auch du dabei warst, aber glücklich entkamst, als ich ihm für sein Schmähen das Fell abzog!"
"Ach, Herr!" flehte das zitternde Lämmchen, "ich bin ja erst vier Wochen alt und kannte meinen Vater gar nicht, so lange ist er schon tot; wie soll ich denn für ihn büßen."
"Du Unverschämter!" so endigt der Wolf mit erheuchelter Wut, indem er die Zähne fletschte. "Tot oder nicht tot, weiß ich doch, daß euer ganzes Geschlecht mich hasset, und dafür muß ich mich rächen."
Ohne weitere Umstände zu machen, zerriß er das Lämmchen und verschlang es.
Das Gewissen regt sich selbst bei dem größten Bösewichte; er sucht doch nach Vorwand, um dasselbe damit bei Begehung seiner Schlechtigkeiten zu beschwichtigen.
Quelle: https://eden.one/fabeln-aesop-das-lamm-und-der-wolf
-
 @ dd664d5e:5633d319
2024-12-29 20:29:03
@ dd664d5e:5633d319
2024-12-29 20:29:03The paparazzi are we

One of the things that bothers me about social media, in general, is that it gives celebrities an air of approachability, that they don't actually offer.
Theoretically, a celebrity could respond to any one of the dozens or even hundreds of people asking them questions or lodging complaints or singing their praises, but they usually only respond very selectively and leave everyone else just sitting there, as a living monument to the ReplyGuy.
And, as a wise man once said, ReplyGuy is a hoe.
Death of a ReplyGuy
This is usually because of time and energy restrictions, but also due to distaste, disdain, or indifference. Regardless of motivation, it is simply the nature of things, when a larger number of people are clamboring for the attention of some particular person.
Ooh, ooh! Can I have the next question?! Would you please address my bug? May I have a microsecond of your time?

Social media (and I include GitHub in this category) ups this game considerably, and potentially turns it all into a dangerous psychological torture, by making us all preoccupied with people who don't interact with us. The most irrational of groupies because we are forever making almost-contact with our stars.
If we can see them talking to one person, we're supposed to feel like they've spoken with all of us. But they haven't. They spoke with someone else, and we were allowed to watch. No different than on television, except that we might be disappointed and eager to return the next day, to renew our futile attempt.
The same intoxicating feeling that playing the lottery elicits. Everyone is a potential winner, but there is only one jackpot. Come back next week. Buy another ticket. This next time, is your time. Promise.
The view from the peanut gallery

It is all an illusion that there is no hierarchy, where there clearly is one. Celebrities of the past had, at least, the decency to remain slightly aloof. But they all want to be one of the Common Folk, now, just as every multi-millionaire aspires to see himself as fundamentally working-class.

All of celebrity social media is a stage, and most of us are merely spectators or commentators, to what is playing on it. This is why, if someone treats me like someone sitting in the peanut gallery, my instinct is to treat them like an actor.
Because, in reality, that is what they are.
-
 @ a42048d7:26886c32
2024-12-27 16:33:24
@ a42048d7:26886c32
2024-12-27 16:33:24DIY Multisig is complex and 100x more likely to fail than you think if you do it yourself: A few years ago as an experiment I put what was then $2,000 worth Bitcoin into a 2 of 3 DIY multisig with two close family members holding two keys on Tapsigners and myself holding the last key on a Coldcard. My thought was to try and preview how they might deal with self custodied multisig Bitcoin if I died prematurely. After over a year I revisited and asked them to try and do a transaction without me. Just send that single Utxo to a new address in the same wallet, no time limit. It could not possibly have failed harder and shook my belief in multisig. To summarize an extremely painful day, there was a literally 0% chance they would figure this out without help. If this had been for real all our BTC may have been lost forever. Maybe eventually a family friend could’ve helped, but I hadn’t thought of that and hadn’t recommended a trusted BTC knowledge/help source. I had preached self sovereignty and doing it alone and my family tried to respect that. I should’ve given them the contact info of local high integrity bitcoiners I trust implicitly. Regardless of setup type, I highly recommend having a trusted Bitcoiner and online resources your family knows they can turn to to trouble shoot. Bookmark the corresponding BTCSessions video to your BTC self custody setup. Multisig is complicated as hell and hard to understand. Complexity is the enemy when it comes to making sure your BTC isn’t lost and actually gets to your heirs. Many Bitcoiners use a similar setup to this one that failed so badly, and I’m telling you unless you’re married to or gave birth to a seriously hardcore maxi who is extremely tech savvy, the risk your Bitcoin is lost upon your death is unacceptably high. My family is extremely smart but when the pressure of now many thousands of dollars was on the line, the complexity of multisig torpedoed them. Don’t run to an ETF! There are answers: singlesig is awesome. From observing my family I’m confident they would’ve been okay in a singlesig setup. It was the process of signing on separate devices with separate signers, and moving a PSBT around that stymied them. If it had been singlesig they would’ve been okay as one signature on its own was accomplished. Do not besmirch singlesig, it’s incredibly powerful and incredibly resilient. Resilience and simplicity are vastly underrated! In my opinion multisig may increase your theoretical security against attacks that are far less likely to actually happen, e.g. an Oceans Eleven style hack/heist. More likely your heirs will be fighting panic, grief, and stress and forget something you taught them a few years back. If they face an attack it will most likely be social engineering/phishing. They are unlikely to face an elaborate heist that would make a fun movie. While I still maintain it was a mistake for Bitkey to not have a separate screen to verify addresses and other info, overall I believe it’s probably the best normie option for small BTC holdings(yes I do know Bitkey is actually multisig, but the UX is basically a single sig). This incident scared me into realizing the importance of simplicity. Complexity and confusion of heirs/family may be the most under-considered aspects of BTC security. If you’ve made a DIY multisig and your heirs can’t explain why they need all three public keys and what a descriptor is and where it’s backed up, you might as well just go have that boating accident now and get it over with.
Once you get past small amounts of BTC, any reputable hardware wallet in singlesig is amazing security I would encourage folks to consider. In a singlesig setup - For $5 wrench attack concerns, just don’t have your hardware signer or steel backup at your home. You can just have a hot wallet on your phone with a small amount for spending.
If you get a really big stack collaborative multisig is a potentially reasonable middle ground. Just be very thoughtful and brutally honest about your heirs and their BTC and general tech knowledge. Singlesig is still great and you don’t have to move past it, but I get that you also need to sleep at night. If you have truly life changing wealth and are just too uncomfortable with singlesig, maybe consider either 1) Anchorwatch to get the potential benefits of multisig security with the safety net of traditional insurance or 2) Liana wallet where you can use miniscript to effectively have a time locked singlesig spending path to a key held by a third party to help your family recover your funds if they can’t figure it out before that timelock hits, 3) Bitcoin Keeper with their automatic inheritance docs and mini script enabled inheritance key. The automatic inheritance docs are a best in class feature no one else has done yet. Unchained charges $200 for inheritance docs on top of your $250 annual subscription, which imho is beyond ridiculous. 4) Swan vault, I’ve generally soured on most traditional 2 of 3 collaborative multisig because I’ve always found holes either in security (Unchained signed a transaction in only a few hours and has no defined time delay, and still doesn’t support Segwit, seriously guys, wtf?), only support signers that are harder to use and thus tough for noobs, or the overall setups are just too complex. Swan Vault’s focus on keeping it as simple as possible really stands out against competitors that tack on unneeded confusion complexity.
TLDR: For small amounts of BTC use Bitkey. For medium to large amounts use singlesig with a reputable hardware wallet and steel backup. For life changing wealth where you just can no longer stomach sinsglesig maybe also consider Anchorwatch, Bitcoin Keeper, Sean Vault, or Liana. Don’t forget your steel backups! Be safe out there! Do your own research and don’t take my word for it. Just use this as inspiration to consider an alternative point of view. If you’re a family of software engineers, feel free to tell me to go fuck myself.
-
 @ b60c3e76:c9d0f46e
2024-05-15 10:08:47
@ b60c3e76:c9d0f46e
2024-05-15 10:08:47KRIS menjamin semua golongan masyarakat mendapatkan perlakuan sama dari rumah sakit, baik pelayanan medis maupun nonmedis.
Demi memberikan peningkatan kualitas layanan kesehatan kepada masyarakat, pemerintah baru saja mengeluarkan Peraturan Presiden (Perpres) nomor 59 tahun 2024 tentang Jaminan Kesehatan. Melalui perpres itu, Presiden Joko Widodo (Jokowi) telah menghapus perbedaan kelas layanan 1, 2, dan 3 dalam Badan Penyelenggara Jaminan Sosial atau BPJS Kesehatan.
Layanan berbasis kelas itu diganti dengan KRIS (Kelas Rawat Inap Standar). Berkaitan dengan lahirnya Perpres 59/2024 tentang Perubahan Ketiga atas Perpres 82/2018 tentang Jaminan Kesehatan, Presiden Joko Widodo telah memerintahkan seluruh rumah sakit yang bekerja sama dengan BPJS Kesehatan melaksanakannya.
Kebijakan baru itu mulai berlaku per 8 Mei 2024 dan paling lambat 30 Juni 2025. Dalam jangka waktu tersebut, rumah sakit dapat menyelenggarakan sebagian atau seluruh pelayanan rawat inap berdasarkan KRIS sesuai dengan kemampuan rumah sakit.
Lantas apa yang menjadi pembeda dari sisi layanan dengan layanan rawat inap sesuai Perpres 59/2024? Dahulu sistem layanan rawat BPJS Kesehatan dibagi berdasarkan kelas yang dibagi masing-masing kelas 1, 2, dan 3. Namun, melalui perpres, layanan kepada masyarakat tidak dibedakan lagi.
Pelayanan rawat inap yang diatur dalam perpres itu--dikenal dengan nama KRIS—menjadi sistem baru yang digunakan dalam pelayanan rawat inap BPJS Kesehatan di rumah sakit-rumah sakit. Dengan KRIS, semua golongan masyarakat akan mendapatkan perlakuan yang sama dari rumah sakit, baik dalam hal pelayanan medis maupun nonmedis.
Dengan lahirnya Perpres 59/2024, tarif iuran BPJS Kesehatan pun juga akan berubah. Hanya saja, dalam Perpres itu belum dicantumkan secara rinci ihwal besar iuran yang baru. Besaran iuran baru BPJS Kesehatan itu sesuai rencana baru ditetapkan pada 1 Juli 2025.
“Penetapan manfaat, tarif, dan iuran sebagaimana dimaksud ditetapkan paling lambat tanggal 1 Juli 2025,” tulis aturan tersebut, dikutip Senin (13/5/2024).
Itu artinya, iuran BPJS Kesehatan saat ini masih sama seperti sebelumnya, yakni sesuai dengan kelas yang dipilih. Namun perpres itu tetap berlaku sembari menanti lahirnya peraturan lanjutan dari perpres tersebut.
Kesiapan Rumah Sakit
Berkaitan dengan lahirnya kebijakan layanan kesehatan tanpa dibedakan kelas lagi, Kementerian Kesehatan (Kemenkes) menegaskan mayoritas rumah sakit di Indonesia siap untuk menjalankan layanan KRIS untuk pasien BPJS Kesehatan.
Kesiapan itu diungkapkan oleh Dirjen Pelayanan Kesehatan Kemenkes Azhar Jaya. “Survei kesiapan RS terkait KRIS sudah dilakukan pada 2.988 rumah sakit dan yang sudah siap menjawab isian 12 kriteria ada sebanyak 2.233 rumah sakit,” ujar Azhar.
Sebagai informasi, KRIS adalah pengganti layanan Kelas 1, 2, dan 3 BPJS Kesehatan yang bertujuan untuk memberikan layanan kesehatan secara merata tanpa melihat besaran iurannya.
Melalui KRIS, rumah sakit perlu menyiapkan sarana dan prasarana sesuai dengan 12 kriteria kelas rawat inap standar secara bertahap. Apa saja ke-12 kriteria KRIS itu?
Sesuai bunyi Pasal 46A Perpres 59/2024, disyaratkan kriteria fasilitas perawatan dan pelayanan rawat inap KRIS meliputi komponen bangunan yang digunakan tidak boleh memiliki tingkat porositas yang tinggi serta terdapat ventilasi udara dan kelengkapan tidur.
Demikian pula soal pencahayaan ruangan. Perpres itu juga mengatur pencahayaan ruangan buatan mengikuti kriteria standar 250 lux untuk penerangan dan 50 lux untuk pencahayaan tidur, temperature ruangan 20--26 derajat celcius.
Tidak hanya itu, layanan rawat inap berdasarkan perpres itu mensyaratkan fasilitas layanan yang membagi ruang rawat berdasarkan jenis kelamin pasien, anak atau dewasa, serta penyakit infeksi atau noninfeksi.
Selain itu, kriteria lainnya adalah keharusan bagi penyedia layanan untuk mempertimbangkan kepadatan ruang rawat dan kualitas tempat tidur, penyediaan tirai atau partisi antartempat tidur, kamar mandi dalam ruangan rawat inap yang memenuhi standar aksesibilitas, dan menyediakan outlet oksigen.
Selain itu, kelengkapan tempat tidur berupa adanya dua kotak kontak dan nurse call pada setiap tempat tidur dan adanya nakas per tempat tidur. Kepadatan ruang rawat inap maksimal empat tempat tidur dengan jarak antara tepi tempat tidur minimal 1,5 meter.
Tirai/partisi dengan rel dibenamkan menempel di plafon atau menggantung. Kamar mandi dalam ruang rawat inap serta kamar mandi sesuai dengan standar aksesibilitas dan outlet oksigen.
Azhar menjamin, Kemenkes akan menjalankan hal tersebut sesuai dengan tupoksi yang ada. “Tentu saja kami akan bekerja sama dengan BPJS Kesehatan dalam implementasi dan pengawasannya di lapangan,” ujar Azhar.
Berkaitan dengan perpres jaminan kesehatan itu, Direktur Utama BPJS Kesehatan Ghufron Mukti menilai, perpres tersebut berorientasi pada penyeragaman kelas rawat inap yang mengacu pada 12 kriteria. "Bahwa perawatan ada kelas rawat inap standar dengan 12 kriteria, untuk peserta BPJS, maka sebagaimana sumpah dokter tidak boleh dibedakan pemberian pelayan medis atas dasar suku, agama, status sosial atau beda iurannya," ujarnya.
Jika ada peserta ingin dirawat pada kelas yang lebih tinggi, kata Ghufron, maka diperbolehkan selama hal itu dipengaruhi situasi nonmedis. Hal itu disebutkan dalam Pasal 51 Perpres Jaminan Kesehatan diatur ketentuan naik kelas perawatan.
Menurut pasal tersebut, naik kelas perawatan dilakukan dengan cara mengikuti asuransi kesehatan tambahan atau membayar selisih antara biaya yang dijamin oleh BPJS Kesehatan dengan biaya yang harus dibayar akibat peningkatan pelayanan.
Selisih antara biaya yang dijamin oleh BPJS Kesehatan dengan biaya pelayanan dapat dibayar oleh peserta bersangkutan, pemberi kerja, atau asuransi kesehatan tambahan.
Ghufron Mukti juga mengimbau pengelola rumah sakit tidak mengurangi jumlah tempat tidur perawatan pasien dalam upaya memenuhi kriteria KRIS. "Pesan saya jangan dikurangi akses dengan mengurangi jumlah tempat tidur. Pertahankan jumlah tempat tidur dan penuhi persyaratannya dengan 12 kriteria tersebut," tegas Ghufron.
Penulis: Firman Hidranto Redaktur: Ratna Nuraini/Elvira Inda Sari Sumber: Indonesia.go.id
-
 @ 6be5cc06:5259daf0
2025-01-21 01:51:46
@ 6be5cc06:5259daf0
2025-01-21 01:51:46Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas.
Satoshi Nakamoto
satoshin@gmx.com
www.bitcoin.org
Resumo
O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado gasto duplo, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações.
As transações são registradas em um livro público chamado blockchain, protegido por uma técnica chamada Prova de Trabalho. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira.
Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu.
1. Introdução
Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em confiança.
Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável.
Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável.
O que precisamos é de um sistema de pagamento eletrônico baseado em provas matemáticas, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas.
Neste documento, apresentamos o Bitcoin, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques.
2. Transações
Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital.
O que é uma assinatura digital?
Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso.
Como funciona na prática?
Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário:
- A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1.
- Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2.
- Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda.
Resolvendo o problema do gasto duplo
Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro.
O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain.
Por que isso é importante?
Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes.
3. Servidor Timestamp
Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica.
Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público.
Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain.
Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada.
O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin.
4. Prova-de-Trabalho
Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente.
A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita.
Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain.
A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos.
Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional.
5. Rede
A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são:
-
Transmissão de Transações: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la.
-
Coleta de Transações em Blocos: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain).
-
Prova-de-Trabalho: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil.
-
Envio do Bloco Resolvido: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede.
-
Validação do Bloco: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos.
-
Construção do Próximo Bloco: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia.
Resolução de Conflitos e Escolha da Cadeia Mais Longa
Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia.
Tolerância a Falhas
A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido.
Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central.
6. Incentivo
O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação.
Recompensa por Mineração
Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho.
Taxas de Transação
Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo.
Incentivo à Honestidade
O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas:
- Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos.
- Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas.
A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema.
Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo.
7. Recuperação do Espaço em Disco
Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações.
Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados.
Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados.
Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo.
8. Verificação de Pagamento Simplificada
É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada.
Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação.
A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede.
Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável.
9. Combinando e Dividindo Valor
No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor.
Entradas e Saídas
Cada transação no Bitcoin é composta por:
- Entradas: Representam os valores recebidos em transações anteriores.
- Saídas: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente.
Normalmente, uma transação contém:
- Uma única entrada com valor suficiente para cobrir o pagamento.
- Ou várias entradas combinadas para atingir o valor necessário.
O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como troco.
Exemplo Prático
Imagine que você tem duas entradas:
- 0,03 BTC
- 0,07 BTC
Se deseja enviar 0,08 BTC para alguém, a transação terá:
- Entrada: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC).
- Saídas: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC).
Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente.
Difusão e Simplificação
A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade.
10. Privacidade
O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando chaves públicas anônimas, que desvinculam diretamente as transações das identidades das partes envolvidas.
Fluxo de Informação
- No modelo tradicional, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário.
- No Bitcoin, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não.
Protegendo a Privacidade
Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas:
- Chaves Públicas Anônimas: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único.
- Prevenção de Ligação: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário.
Riscos de Ligação
Embora a privacidade seja fortalecida, alguns riscos permanecem:
- Transações multi-entrada podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total.
- O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas.
11. Cálculos
Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito.
Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira.
Mas isso é extremamente difícil.
Como o Ataque Funciona
Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido.
- Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira.
- O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida.
Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente.
A Corrida Entre Cadeias
Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos.
Suponha que:
- A rede honesta tem 80% do poder computacional (ou seja, resolve 8 de cada 10 quebra-cabeças).
- O atacante tem 20% do poder computacional (ou seja, resolve 2 de cada 10 quebra-cabeças).
Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar.
Por Que o Ataque Fica Cada Vez Mais Improvável?
Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos:
P = (q/p)^z
- q é o poder computacional do atacante (20%, ou 0,2).
- p é o poder computacional da rede honesta (80%, ou 0,8).
- z é a diferença de blocos entre a cadeia honesta e a cadeia do atacante.
Se o atacante está 5 blocos atrás (z = 5):
P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%)
Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável.
Se ele estiver 10 blocos atrás (z = 10):
P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%).
Neste caso, as chances de sucesso são praticamente nulas.
Um Exemplo Simples
Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível.
No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática.
Por Que Tudo Isso é Seguro?
- A probabilidade de sucesso do atacante diminui exponencialmente. Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema.
- A cadeia verdadeira (honesta) está protegida pela força da rede. Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar.
E Se o Atacante Tentar Continuar?
O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil.
Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso.
12. Conclusão
Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos.
Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
-
 @ a4a6b584:1e05b95b
2024-12-26 17:13:08
@ a4a6b584:1e05b95b
2024-12-26 17:13:08Step 1: Secure Your Device
- Install an Antivirus Program
Download and install a trusted antivirus program to scan files for potential malware. - For Linux: Calm Antivirus
-
For Windows: CalmWin Antivirus
-
Install a VPN
A VPN is essential for maintaining privacy and security. It will encrypt your internet traffic and hide your IP address. -
Recommended: Mullvad VPN, which accepts Bitcoin for anonymous payment.
-
Install a Torrent Program
You’ll need a torrent client to download files. -
Recommended: Deluge
-
Install the Tor Browser
To access The Pirate Bay or its proxies, you’ll need the privacy-focused Tor Browser.
Step 2: Prepare Your Setup
- Ensure your VPN is running and connected.
- Open the Tor Browser.
- Launch Deluge to have your torrent client ready.
Step 3: Using Tor Go to The Pirate Bay via Onion Service or Find a Trusted Pirate Bay Proxy
Accessing The Pirate Bay directly can be challenging due to restrictions in some regions. Proxy sites often fill the gap. - The Pirate Bay Onion service: http://piratebayo3klnzokct3wt5yyxb2vpebbuyjl7m623iaxmqhsd52coid.onion - Or find a trusted proxy: Use a site like Pirateproxy or a reliable Tor directory for updated lists.
Step 4: Search for Linux Distros
- On The Pirate Bay, navigate to the "OtherOS" category under the Applications section.
- Enter your desired Linux distro in the search bar (e.g., "Ubuntu," "Arch Linux").
Step 5: Select a Torrent
- Filter the Results:
- Look for torrents with the highest seeders (SE) and the fewest leechers (LE).
-
Trusted users are marked with a green skull icon—these are usually safe uploads.
-
Copy the Magnet Link:
- Right-click on the magnet icon next to the trusted torrent and select "Copy Link."
Step 6: Start the Download
- In Deluge, paste the copied magnet link into the “Add Torrent” box.
- Click OK to start the download.
- Monitor the progress until the download completes.
Step 7: Scan the Downloaded File
Once the file is downloaded: 1. Scan for viruses: Right-click the file and use Calm or CalmWin to verify its integrity.
2. If the file passes the scan, it’s ready for use.
Step 8: Manage Your File
- Seed or Remove:
- To help the torrent community, keep seeding the file by leaving it in your torrent client.
-
To stop seeding, right-click the file in Deluge and remove it.
-
Move for Long-Term Storage: Transfer the file to a secure directory for regular use.
Notes on Safety and Ethics
- Verify Legitimacy: Ensure the torrent you are downloading is for an official Linux distribution. Torrents with unusual names or details should be avoided.
- Support the Developers: Consider visiting the official websites of Linux distros (Ubuntu, Arch Linux) to support their work directly.
By following these steps, you can safely and privately download Linux distributions while contributing to the open-source community.
- Install an Antivirus Program
-
 @ bbb5dda0:f09e2747
2025-01-13 12:16:00
@ bbb5dda0:f09e2747
2025-01-13 12:16:00This is my first attempt of regularly reviewing my week (currently, week 2) and I want to take you along for it.
This week was one where I was rebooting after all the festivities, personal obligations and a bit of travel! First, I worked on getting back on some comments on my proposals on NIP-42 and the Transport Method Announcement NIP.
NIP-42 proposal
The responses to the proposal of the NIP-42 exstension confused me a bit, my interpretation of nip42 AUTH was both authentication and authoriziation. But as it turns out people only want authentication to be part of this NIP, which is understandable. I'm wondering what other structure should be used for authorization then. I thought this would be a great place because of the similar allow/disallow mechanism that applies to both authentication and authorization.
I get the argument that authorization would need to be handled somewhere else. In my case i want authorization by payment. meaning there is no Authentication, we don't care who it is.
I worked out this comment, to see what other options would come up. https://github.com/nostr-protocol/nips/pull/1609#issuecomment-2577243988
Evaluating current state Epoxy
It's been a little bit since I made any progress on epoxy, but this week i'm picking it back up. So i'm trying to see what my next steps on it will be. I thought first maybe i need to add the random delays, but that's in the bigger scheme of things a 'nice to have'. I should probably first work on fixing the nightmare that is unencrypted traffic. And for that, i need pubkey addressing to work properly.
Evaluating current state CI/CD
This week i met up with Auggie, who's quite knowledgable into CI/CD stuff. I think a cool short-term goal for myself is to get an automated build and publish of the epoxy docker container. That shouldn't be too hard to attain, but I needed to refresh my memory on what I last worked on for a bit.
I realized that that was a very hacky approach and i really want to know Auggie's perspective on it. I came across his comment on my blogpost about it which i'd missed earlier. My doubt is wether i should try to rebuild what CI/CD is from scratch, but nostr-native. Or should I strive to have something backwards-compatible and use existing GitHub/Gitea runners?
In our call we settled on trying to get the runner approach working and see how we go from there. I'd work out a GitHub action so we could upload artifacts to Blossom and he'd look into the inner workings of Gittea as he had worked on the stack before.
Blossom uploads GitHub action
I tried to move forward on the Blossom uploads on friday but got stuck on imports that would just not resolve on the github action (
ERR_PACKAGE_PATH_NOT_EXPORTED). Long story short, I was just not bundling my build properly and (spoiler) worked this out on Monday.In short
Quite an alright week, ramping up my efforts now and i'm exited for what's coming. See you next week!
-
 @ ed84ce10:cccf4c2a
2025-01-13 06:48:47
@ ed84ce10:cccf4c2a
2025-01-13 06:48:470. BUIDL AI
In the age of AI, where technology moves faster than our ability to comprehend its implications, DoraHacks stands at the intersection of creation and disruption. It is not just a platform; it is a movement—a global network of individuals solving fascinating problems, building the boldest ideas, and pushing the limits of what’s possible. DoraHacks is also on a trajectory to become the most significant Agentic Community Platform in the world, automating hackathons, and open-source communities across the globe.
1. Everyone will be a Hacker
Let’s start with a fundamental shift in understanding. The term “hacker” has long been burdened by the weight of misconception. Too often, it evokes images of shady figures hunched over keyboards, hacking into systems in the dead of night. But in truth, the hacker is something entirely different—and far more important.
A hacker is a builder. A creator. Someone who, when faced with a problem, doesn’t wait for permission or perfect conditions. Instead, they use ingenuity, resourcefulness, and relentless curiosity to solve it.
When DoraHacks launched in 2014, it embraced this ethos wholeheartedly. Its mission was to unite hackers worldwide to tackle humanity’s most pressing challenges. These hackers weren’t confined to coders; they included designers, entrepreneurs, scientists, and anyone driven by a desire to create meaningful change.
Fast forward to 2025, and we’re witnessing a seismic shift in how work and innovation are done. AI is automating the repetitive and mundane, from office tasks to driving, freeing humanity to focus on the creative and the essential. In this new world, everyone will be a hacker—leveraging AI to build, design, and solve problems that matter. DoraHacks, already the world’s largest hacker ecosystem with over 200,000 builders, is perfectly positioned to scale this movement a thousandfold.
2. From Hacker Movement to Freedom of BUIDL
DoraHacks has always been a platform for builders, but its vision extends far beyond hackathons and prize pools. At its core lies a principle that has the power to reshape the world: Freedom of BUIDL.
Freedom of BUIDL is more than the ability to create. It is the removal of barriers—geographical, financial, institutional—that prevent people from realizing their potential. The extraordinary success of Silicon Valley over the last century was built on precisely this freedom: a culture and infrastructure that allowed the world’s brightest minds to converge, collaborate, and innovate without limits.
However, this opportunity is not distributed equally. A young builder in rural Africa, a student in Southeast Asia, or a refugee in Europe may have the talent and drive to build transformative solutions but lack the resources or networks to do so. DoraHacks aims to democratize innovation by creating a global platform where anyone, anywhere, can participate in the Freedom of BUIDL.
Consider this: a team in Nairobi uses AI to design sustainable energy grids, collaborating with developers in Berlin and advisors in Silicon Valley—all made possible by DoraHacks. This is not the future; it’s happening now. And it’s just the beginning.
3. The Cutting Edge of the Cutting Edge
What makes DoraHacks unique is not just its scale but its relentless focus on the frontier of open-source technology. From application-specific blockchains to quantum computing software infrastructures and open-source space technology, DoraHacks has consistently championed what’s next.
In 2025, projects using decentralized governance models powered by intelligent agents will begin to emerge, transforming the way open-source communities coordinate and the way new technologies accelerate, from consumer appchains to decentralized social media, from memes to quantum software, from biohacks to open-source space tech.
In the years to come, DoraHacks has the potential be the birthplace of many of the world’s most transformative open-source platform technologies. It will be the launchpad for breakthroughs that redefine how we live, work, and connect.
4. BUIDL AI: The Intelligence Behind the Ecosystem
At the heart of this transformation lies BUIDL AI, one of DoraHacks’ most ambitious undertakings yet. As the hacker ecosystem grows, so too does the complexity of its needs. Builders require mentorship, funding, collaborators, and access to cutting-edge tools. BUIDL AI is the intelligence layer that makes this possible.
Imagine an AI that doesn’t just analyze trends but anticipates them, matching hackers with the exact resources, mentors, and collaborators they need at the right time, helping them to join the BUIDL teams that best fit their skill sets and aspirations. Imagine a system that optimizes resource allocation across tens of thousands of projects, ensuring that the most promising ideas get the support they deserve. This is not speculative; it’s the foundation DoraHacks is building today.
As these tools mature, they will enable DoraHacks to evolve into a full-fledged Agentic Community Platform—one that operates with the intelligence, speed, and adaptability required to shape the future.
5. Conclusion: Building for the Builders of Tomorrow
When the creators of Doraemon imagined a robot that could solve any problem, they were unknowingly inspiring a generation to dream bigger. Today, DoraHacks takes up that mantle, not as fiction but as a reality: a platform where the builders of the future are empowered to create the tools, technologies, and systems that will change everything.
We stand at the crossroads of a new era. AI, blockchain, and quantum computing are converging, new frontiers are opening, and the opportunities are boundless. DoraHacks will be there, championing the hackers, builders, and dreamers who dare to take humanity’s next leap forward.
In the end, the future belongs to the builders. And the world they build will be extraordinary.
-
 @ 266815e0:6cd408a5
2024-05-09 17:23:28
@ 266815e0:6cd408a5
2024-05-09 17:23:28Lot of people are starting to talk about building a web-of-trust and how nostr can or is already being used as such
We all know about using the kind:3 following lists as a simple WoT that can be used to filter out spam. but as we all know it does not really signal "trust", its mostly just "I find your content interesting"
But what about real "trust"... well its kind of multi-denominational, I could trust that your a good developer or a good journalist but still not trust you enough to invite you over to my house. There are some interesting and clever solutions proposed for quantifying "trust" in a digital sense but I'm not going to get into that here. I want to talk about something that I have not see anyone discuss yet.
How is the web-of-trust maintained? or more precisely how do you expect users to update the digital representation of the "trust" of other users?
Its all well and good to think of how a user would create that "trust" of another user when discovering them for the first time. They would click the "follow" button, or maybe even rate them on a few topics with a 1/5 star system But how will a user remove that trust? how will they update it if things change and they trust them less?
If our goal is to model "trust" in a digital sense then we NEED a way for the data to stay up-to-date and as accurate as possible. otherwise whats the use? If we don't have a friction-less way to update or remove the digital representation of "trust" then we will end up with a WoT that continuously grows and everyone is rated 10/10
In the case of nostr kind:3 following lists. its pretty easy to see how these would get updated. If someone posts something I dislike or I notice I'm getting board of their content. then I just unfollow them. An important part here is that I'm not thinking "I should update my trust score of this user" but instead "I'm no longer interested, I don't want to see this anymore"
But that is probably the easiest "trust" to update. because most of us on social media spend some time curating our feed and we are used to doing it. But what about the more obscure "trust" scores? whats the regular mechanism by which a user would update the "honestly" score of another user?
In the real world its easy, when I stop trusting someone I simply stop associating with them. there isn't any button or switch I need to update. I simply don't talk to them anymore, its friction-less But in the digital realm I would have to remove or update that trust. in other words its an action I need to take instead of an action I'm not doing. and actions take energy.
So how do we reflect something in the digital world that takes no-energy and is almost subconscious in the real world?
TLDR; webs-of-trust are not just about scoring other users once. you must keep the score up-to-date
-
 @ fbf0e434:e1be6a39
2025-01-20 06:35:18
@ fbf0e434:e1be6a39
2025-01-20 06:35:18Hackathon 摘要
Watson Code Fest 2024 是一项年度生物Hackathon,由加德满都大学合作组织,重点关注医疗保健和信息学。此次活动汇集了41位开发者,他们致力于30个创新项目,旨在将生物技术、计算机科学和医疗保健整合,解决全球及本地的医疗保健挑战。探索的关键领域包括个性化医疗、智能医疗系统、诊断中的AI以及公共卫生数据分析。
该Hackathon的主要目标是促进创新、推广多学科合作,并增强技能发展。它为学生、专业人士和来自各个领域的研究人员提供了一个合作的环境,强调信息学在推进医疗解决方案中的角色。
活动在加德满都大学举行,为期两天,鼓励参与者创造性思考和协作工作。其旨在弥合学术界与工业界之间的差距,激发创新并促进网络建设。这次Hackathon的影响在于其激发新医疗技术的能力以及在尼泊尔培养创新文化,且具有潜在的全球影响。
Hackathon 获奖者
1st Place Prize Winners
- MutraSuchak : 该项目通过适用于医疗应用的低成本方法促进早期阿尔茨海默病的检测。它集成了ESP模块和Python Flask服务器,开源资源可在GitHub上获得。
Runner-Up Prize Winners
- PCOSgen: 该项目编制了一份用于PCOS表型的预测数据库,有助于早期诊断和个性化治疗。它使用数据驱动方法解决研究差距并改进患者结果。
Most Innovative Project Prize Winners
- Silent Witness: Graph-Based Abuse Detection: 该计划使用AI分析来自摄像头的面部表情以检测虐待模式。通过使用YOLO模型来保护隐私,它构建交互图以识别和标记负面模式,同时促进积极的环境。
有关所有参赛项目的详细列表,请访问 Watson Code Fest's project page。
关于组织者
Kathmandu University Biotechnology Creatives
加德满都大学生物技术创意(KUBiC)是生物技术和生物信息学领域的先锋组织。KUBiC以举办年度Watson Code Fest而闻名,为创新者、程序员和创造性思考者提供了一个平台,以解决这些领域中的关键挑战。KUBiC坚定致力于推进生物科学,在促进合作和创造力方面表现出色。其使命是重新定义生物学的未来,并推动跨学科领域的进步。更多信息可在其网站上找到。
-
 @ df478568:2a951e67
2025-01-20 05:23:36
@ df478568:2a951e67
2025-01-20 05:23:36I took this picture at about block 416,220(June 13, 2016). The price of eggs on that day was $1.99, 16.5¢ per egg if you still measure stuff with the broken ruler we call fiat. What if we measured the price in sats instead? I found the price on that date from the bitbo calender. According to this website, $1.99 was worth 260,000 sats back then. Each egg cost 21,667 sats! Oh My Zeus!😱

I used this mempool calculator to see how much that is today. Turns out that it's $272.88 as of block 879,943. Since the fiat ruler is broken, the price of a dozen eggs also has NGU. I took this picture the last time I went to the grocery store. Eggs cost enough to shock fiat maxis. $8.99 OMZ!😱
What does a dozen eggs cost if you ignore the broken ruler? 8,572 sats today, just 714 sats per egg. Holy Wiemar Republic Batman! That's 30X cheaper! 😁
For some strange reason I can't pretend to understand, the Federal reserve tracks the price of eggs denominated in bitcoin. I guess they want to stay humble and stack money printer go brrrrrr. You can see the price of eggs drop off a cliff like Wile E Coyote on their website.
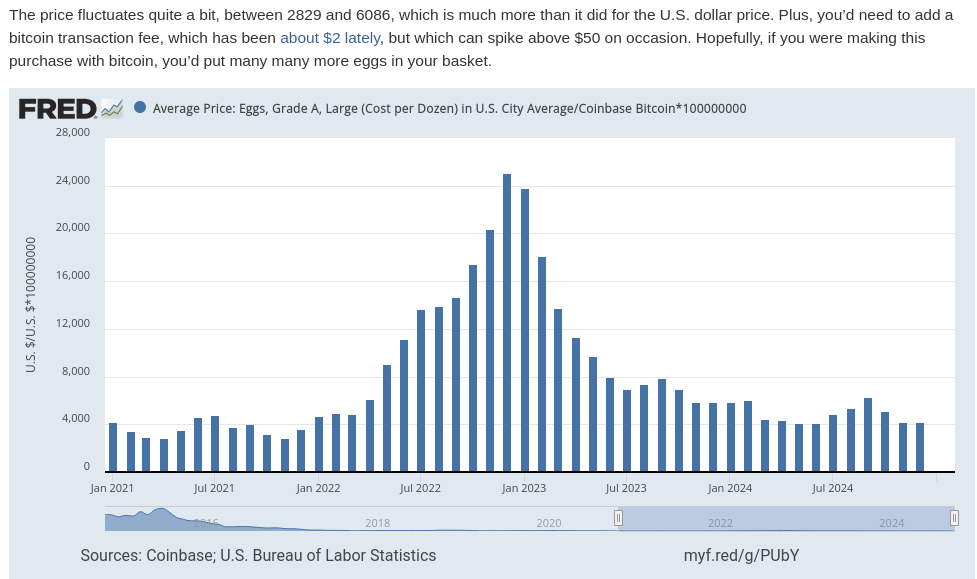
In The Price of Tommorrow and too many podcasts to mention, Jeff Booth argues the free market makes things cheaper over time, but the fiat syatem is syatematic theft. This theft occurs via inflation, which is really wage deflation. In other words, eggs are getting cheaper over time because egg producers become more efficient. We see tye fruits of this efficiency in Big screen TV's because the fiat price gets cut in half every ten years or so, but this is also a product of a broken ruler. The TV is probably 60X cheaper in bitcoin terms. It makes sense, TV's don't get bird flu, but when you begin using bitcoin as your unit of account, the measurement of value makes more sense than fiat clown world on the broken ruler standard. I remember when coffee was 100,000 sats. Now it's 16,699 sats. Living on the sat standards allows you to see Jeff Booth's thesis play out in real time

Life Gets More Expensive On The Broken Ruler Standard
I see so many young people on the broken ruler standard bemoan about food and housing prices. There are people with master's degrees who have already lost hope of buying a single family home and achieving the "American dream." To be honest, I would be pretty bummed about it too if I was on the broken ruler standard. A few months ago I spoke with a woman who made at least twice as much fiat as I do say, "I hope this housing market crashes so I can buy a house!"
That's sad. I have a lot of empathy for that feeling. Since the great financial crisis, I've only been able to get part time work, but my family wqs able to get a mortgage worth 12.5 bitcoin at the so-called "height of the market." We put as little money down as possible, 3% and I sold my old 401k for that "money." I also used some of it for repairs and taxes, but went all-in on bitcoin with everything else. Now our house is worth about 5 bitcoin. The way I see it, real estate is always crashing.
People on the broken ruler standard cry, "Wah, Wah. I hope there's a housing crash! Wah! Wah! Muh egg prices!" Buy a brand spanking new car for $50,00 car with a 7% interest rate and they will say, "Congratulations!" The trouble is, the price of the car falls like eggs compared to bitcoin on the broken ruler standard. This is because prices are distorted when measured in a broken ruler standard.
Get Off The Broken Ruler Standard
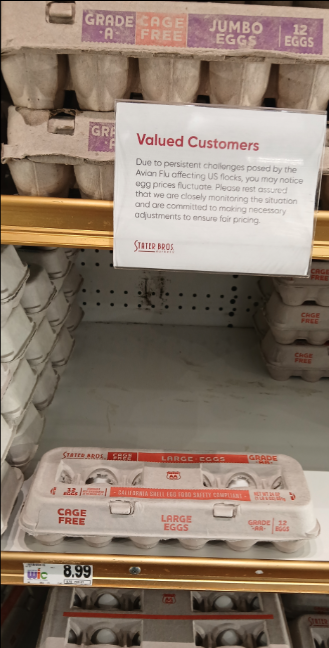
Before I met my wife, I played poker to supplement my income. I don't play much anymore, but poker taught me about risk management, probability, game theory, and many other things applicable to bitcoin. Poker gave me the background knowledge I needed to study bitcoin. In a sly, round-about way , poker taught me how to spend less bitcoin than I make. In traditional technical finance terminology, this is called "fucking saving." If you were not taught how to save and spend more than you earn, no matter how many broken ruler bucks you may earn, bitcoin will not work for you.
My wife makes a lot of broken ruler bucks. Unfortunately, we were broke in 2016 because we both were in school. Nevertheless, I'm proud of my stack amd I'm now at a point in life where I can get paid in bitcoin with very little risk because of my sugar mama, I mean wife, gets paid very well.
I spend like almost every other American consumer, plastic broken ruler debt cards. I put my little Strike ACH number on the Discover app. I keep a couple million sats on Strike and pay my credit card every month. In other words, I use Strike like a four-letter word: bank.
Sometimes I'll get a craving for tacos., I've never found a food truck that takes bitcoin, but they often use the Cash App. People on the broken ruler standard can't instantaneously send broken ruler bucks from PayPal to Zelle and vice-versa. They must first send broken ruler bucks from PayPal to the bank and then send the broken ruler bucks through Zelle. I can send sats directly from Strike to thr Cash App within seconds.
Sats As A Unit Of Account
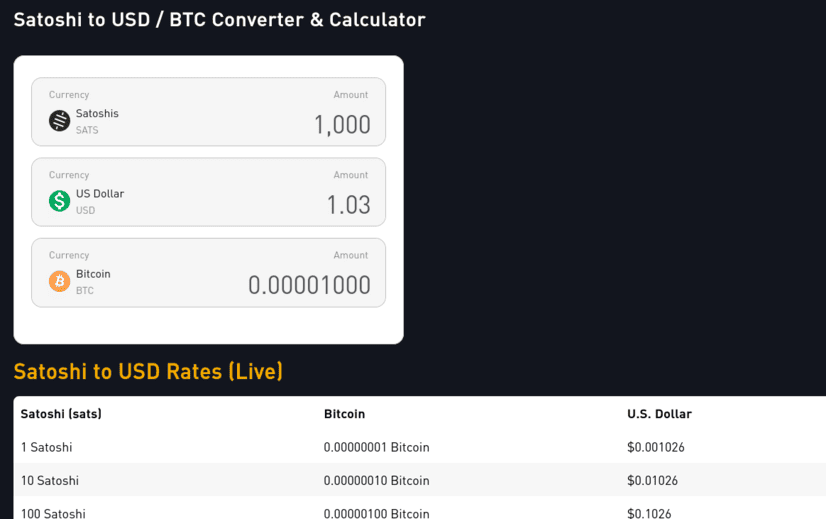
The price of bitcoin fluctuates which makes it difficult to use as a unit of account. Who wants to divide the price of bitcoin by 100 million. Ain't nobody got time for that. If a whole coin costs 100k, then 1,000 sats = $1.00. This means each 100 sats is worth 10¢. 10 sats = 1¢. If the price drops 50%, 1000 sats is 50¢. If it does a 10X, $1,000 sats is $10.00. Living on a sat standard requires a little math, but it's easy to estimate. For more precise calculations I use mem pools calculator.
Money is a store of value, medium of exchange, and unit of account. If you use bitcoin on all three ways, you are using bitcoin as money. Saving becomes spending less bitcoin, not "buying more bitcoin." If you stack sats, your goal should be to leave the broken ruler standard and adopt sats as the standard. The world will still price your sats with a broken ruler. Sometimes this broken ruler makes you look like a fool. Other times, the broken ruler makes you look like a genius. Therefore, you must stay humble and stack sats.
You'll need some savings before you can deal with the broken ruler fallacy, but once you consistently stack sats and NGU continues to U, you'll eventually see life gets easier when you make sats the standard.
I will sell some sats to pay for my food and I send a tip to the food trucker in bitcoin using the Cash App gift button. It is actually very easy for them to accept bitcoin. They just don't know it yet. I don't proselytize the gospel of our lord and savior Satoshi Nakamoto. I just send them a few thousand sats. Good orange pilling is like good writing: Show, don't tell.
Does it require KYC?
Yeah, but so does Bank of Broken Rulers.
Haven't you heard the phrase, not your keys, not your bitcoin?
Yes. It's true. The 2 million sats or so is "not my bitcoin." From my perspective, however, it is the least risky way of paying my bills. I believe it is less risky than keeping broken ruler bucks in a bank. FDIC insurance sounds nice as canceled Insurance policies in the Pacific Palisades.
I could keep my 2 million sats in self-custody in my own lightning wallet. I could use Zap Planner to schedule my payments to hit Strike moments before I pay my bill, but I know me. I've lost sats on the lightning network before. I am more likely to lose the sats on my self-custodial lightning wallet than lose them because Strike could possibly rug-pull me. So for now, I just keep 2 million sats on the app. If bitcoin does a 10X, I'll keep 200,000 sats on Strike. If it drops 50%, I will keep 4 million sats on there.
I typically spend between $600- $1,000 in broken ruler bucks a month. This doesn't include my mortgage or food. My wife pretty much covers that stuff. Life happens though. Sometimes I need to pay a plumber, or a roofer or something, but most months, I have a sat surplus, a phenomena I like to call sats savings. My fiat check converts to bitcoin right on payday. I pay my credit cards off that day. If the sats are worth a little more, I pay taxes on that little bit. To make the math easy, say I get paid $1,000 on Friday. When I pay my bills, The broken ruler measurement now says I have $1,100. I pay my credit card. I owe capital gains on that $100 worth of sats. If my paycheck happens to be worth $900,I don’t pay any taxes because I have a loss. I won’t lie. I still get a bit perturbed when the price goes down 10% on payday, but it’s not the end of the world. If it doesn’t go back up by next payday, good. I earn more sats. If it goes up by next payday, good. All the sats I stacked before can buy more groceries.
Get On The Sats Standard
!;make sats the standard](https://gitea.marc26z.com/marc/BlogImprovementProposals/raw/branch/main/pics/Screenshot%20from%202025-01-19%2020-35-55.png)
Making sats the standard does this for the individual on the microeconomic level. Each Bitcoiner gradually accumulates sats. Stack long enough, study long enough, and experience enough 80% dips and you too will develop an unwavering conviction. You get paid in sats. You spend sats. You save sats. You no longer give a damn about your local fiat currency. A dozen eggs cost less than half of a single egg cost 8 years ago. If you lose 50% of your spending power overnight, you can buy less eggs, but a dozen eggs still costs less than 1 egg 8 years ago. Bitcoin is just better money.
If my fiat bank account takes more money out than I have in it, I can do an instant withdrawl on Strike. The fiat appears in my fiat bank account instantly. No more waiting 3-5 days for the money to get there. The bank does not get to keep charging you overdraft fee after overdraft fee for every little transaction. Bitcoin just works better. You can send it all over the world within seconds. You can buy stuff online with it or pay your credit cards. There is literally no reason to hold dollars anymore if you don’t want to. When you’re ready, make sats the standard. If you are not ready, keep stacking.
Onward.
-
 @ fd208ee8:0fd927c1
2024-12-26 07:02:59
@ fd208ee8:0fd927c1
2024-12-26 07:02:59I just read this, and found it enlightening.
Jung... notes that intelligence can be seen as problem solving at an everyday level..., whereas creativity may represent problem solving for less common issues
Other studies have used metaphor creation as a creativity measure instead of divergent thinking and a spectrum of CHC components instead of just g and have found much higher relationships between creativity and intelligence than past studies
https://www.mdpi.com/2079-3200/3/3/59
I'm unusually intelligent (Who isn't?), but I'm much more creative, than intelligent, and I think that confuses people. The ability to apply intelligence, to solve completely novel problems, on the fly, is something IQ tests don't even claim to measure. They just claim a correlation.
Creativity requires taking wild, mental leaps out into nothingness; simply trusting that your brain will land you safely. And this is why I've been at the forefront of massive innovation, over and over, but never got rich off of it.
I'm a starving autist.
Zaps are the first time I've ever made money directly, for solving novel problems. Companies don't do this because there is a span of time between providing a solution and the solution being implemented, and the person building the implementation (or their boss) receives all the credit for the existence of the solution. At best, you can hope to get pawned off with a small bonus.
Nobody can remember who came up with the solution, originally, and that person might not even be there, anymore, and probably never filed a patent, and may have no idea that their idea has even been built. They just run across it, later, in a tech magazine or museum, and say, "Well, will you look at that! Someone actually went and built it! Isn't that nice!"
Universities at least had the idea of cementing novel solutions in academic papers, but that: 1) only works if you're an academic, and at a university, 2) is an incredibly slow process, not appropriate for a truly innovative field, 3) leads to manifestations of perverse incentives and biased research frameworks, coming from 'publish or perish' policies.
But I think long-form notes and zaps solve for this problem. #Alexandria, especially, is being built to cater to this long-suffering class of chronic underachievers. It leaves a written, public, time-stamped record of Clever Ideas We Have Had.
Because they are clever, the ideas. And we have had them.
-
 @ 6e468422:15deee93
2024-12-21 19:25:26
@ 6e468422:15deee93
2024-12-21 19:25:26We didn't hear them land on earth, nor did we see them. The spores were not visible to the naked eye. Like dust particles, they softly fell, unhindered, through our atmosphere, covering the earth. It took us a while to realize that something extraordinary was happening on our planet. In most places, the mushrooms didn't grow at all. The conditions weren't right. In some places—mostly rocky places—they grew large enough to be noticeable. People all over the world posted pictures online. "White eggs," they called them. It took a bit until botanists and mycologists took note. Most didn't realize that we were dealing with a species unknown to us.
We aren't sure who sent them. We aren't even sure if there is a "who" behind the spores. But once the first portals opened up, we learned that these mushrooms aren't just a quirk of biology. The portals were small at first—minuscule, even. Like a pinhole camera, we were able to glimpse through, but we couldn't make out much. We were only able to see colors and textures if the conditions were right. We weren't sure what we were looking at.
We still don't understand why some mushrooms open up, and some don't. Most don't. What we do know is that they like colder climates and high elevations. What we also know is that the portals don't stay open for long. Like all mushrooms, the flush only lasts for a week or two. When a portal opens, it looks like the mushroom is eating a hole into itself at first. But the hole grows, and what starts as a shimmer behind a grey film turns into a clear picture as the egg ripens. When conditions are right, portals will remain stable for up to three days. Once the fruit withers, the portal closes, and the mushroom decays.
The eggs grew bigger year over year. And with it, the portals. Soon enough, the portals were big enough to stick your finger through. And that's when things started to get weird...
-
 @ 16d11430:61640947
2025-01-20 03:32:57
@ 16d11430:61640947
2025-01-20 03:32:57Building a business, especially in the Bitcoin ecosystem, requires an unwavering commitment to patience and a deep belief in the fundamentals that underpin the technology. In a world driven by short-term profits and speculative fervor, it is easy to lose sight of the long game. Yet, the path to creating something meaningful and enduring often lies in resisting the noise and staying true to core principles.
The Bitcoin Revolution: Planting Seeds in Fertile Soil
Bitcoin is not just a technological innovation; it is a paradigm shift in how we view money, value, and trust. For entrepreneurs, it offers an opportunity to align their work with a monetary system that is decentralized, censorship-resistant, and designed for fairness. However, building a business in the Bitcoin space requires a recognition that societal adoption takes time.
As the saying goes, "The pot has to boil further." The ecosystem is still maturing, and while the signs of progress are undeniable, there is much work to be done. For plebs—the passionate individuals who embrace Bitcoin as a way of life—to eagerly work for sats, the economic incentives must become undeniable. This requires building infrastructure, educating the masses, and proving the utility of Bitcoin beyond speculation.
The Role of Patience in Entrepreneurship
Patience is not passive. It is an active process of nurturing your business, learning from setbacks, and steadily improving your product or service. In the Bitcoin space, patience involves:
-
Education and Advocacy: Many people still misunderstand Bitcoin's potential. Entrepreneurs must invest time in educating their audience, building trust, and explaining why Bitcoin is a better alternative.
-
Incremental Growth: Bitcoin adoption happens at the margins before reaching critical mass. Businesses that focus on steady growth rather than explosive, unsustainable expansion are more likely to succeed in the long run.
-
Long-Term Vision: Building for Bitcoin means thinking in decades, not quarters. A business grounded in sound principles—honesty, resilience, and utility—can weather market cycles and emerge stronger.
Faith in Fundamentals
Bitcoin’s fundamentals are its greatest strength: fixed supply, decentralized governance, and security. These principles create a monetary system that is fair and immune to corruption. Entrepreneurs in this space must build businesses that reflect these same values.
Integrity: A Bitcoin business should prioritize transparency and fairness, aligning incentives with customers and stakeholders.
Resilience: Bitcoin thrives in adversity. Businesses in this ecosystem should adopt a similar mindset, designing products that endure volatility and uncertainty.
Utility: Focus on solving real problems for real people. Whether it’s offering Bitcoin payments, facilitating education, or building tools for sovereignty, utility drives adoption.
Letting the Pot Boil: Creating Conditions for Change
The conditions necessary for mainstream Bitcoin jobs will emerge when the ecosystem matures further. This requires collaboration between businesses, developers, and advocates to:
Expand Infrastructure: Lightning Network, wallet solutions, and Bitcoin-native applications are critical to making Bitcoin more accessible and user-friendly.
Incentivize Participation: Paying workers in sats is not just a gimmick—it is a way to demonstrate Bitcoin’s superiority as a store of value and medium of exchange.
Build Culture: Bitcoin is more than technology; it is a movement. Businesses must contribute to a culture of empowerment, self-sovereignty, and fairness.
Conclusion: The Time Will Come
Faith in fundamentals is what separates builders from speculators. While the market will inevitably test your resolve, the rewards for those who persevere are immense. The time for mainstream Bitcoin jobs will come, but only when the ecosystem is ready—when plebs are eager to work for sats not out of necessity, but because it is the natural choice in a world aligned with Bitcoin's principles.
Until then, entrepreneurs must remain patient, continue building, and trust in the vision of a decentralized future. The pot will boil. When it does, those who believed in the fundamentals will be the ones to shape the next era of economic freedom.
-
-
 @ 58937958:545e6994
2025-01-13 03:31:48
@ 58937958:545e6994
2025-01-13 03:31:48I made croquettes inspired by Spiral's character "Bitcoin (Puppet)."

The method is the same as making regular croquettes. I also tried making a version (right) with the arms and legs attached while shaping the filling, but they fell off before I could coat them in flour.

The face is made with seaweed and sliced cheese. The arms and legs are made with fish cake (hanpen). I brushed soy sauce on the legs and lightly toasted them in a toaster, which gave them a brown color.
 The arms and legs are attached using thin spaghetti.
When I searched for character-themed bentos (kyaraben), I came across the idea of using dried pasta, which made sense.
I used fried spaghetti sticks for attachment.
The arms and legs are attached using thin spaghetti.
When I searched for character-themed bentos (kyaraben), I came across the idea of using dried pasta, which made sense.
I used fried spaghetti sticks for attachment.Here’s Bitcoin Croquette squished into a bento box:

Halving

Notes
- I tried freezing the filling to help it hold its shape, but it backfired. It stuck to the plate and the cooking paper, and once partially thawed, it became way too watery. Freezing might work with better preparation.
- The filling was quite dry when shaping, so it might be better to add a binder (this time, I only used potatoes and sautéed onions).
The shape of Bitcoin Puppet was really easy and fun to make, so I’d love to try creating something else next time!
nostr:nevent1qqsxgpjvf9g9suhzx5asqhvnlvnarl43kuhas8v5g2ryjr9yjjp0z5ctkh5pt
-
 @ ed84ce10:cccf4c2a
2025-01-20 06:24:04
@ ed84ce10:cccf4c2a
2025-01-20 06:24:04Hackathon Summary
The Watson Code Fest 2024, an annual biohackathon, was organized in collaboration with Kathmandu University, with a focus on healthcare and informatics. The event brought together 41 developers who worked on 30 innovative projects, aiming to integrate biotechnology, computer science, and healthcare to tackle both global and local healthcare challenges. Key areas of exploration included personalized medicine, smart healthcare systems, AI in diagnostics, and public health data analysis.
The hackathon's primary objectives were to foster innovation, promote multidisciplinary collaboration, and enhance skill development. It provided a collaborative environment for students, professionals, and researchers from various fields, underscoring the role of informatics in advancing healthcare solutions.
Held at Kathmandu University over two days, the event encouraged participants to think creatively and work collaboratively. It sought to bridge the gap between academia and industry, stimulate innovation, and foster networking. The hackathon's impact was evident in its ability to inspire new healthcare technologies and cultivate a culture of innovation in Nepal, with potential global implications.
Hackathon Winners
1st Place Prize Winners
- MutraSuchak: This project facilitates early Alzheimer's detection through cost-effective methods suitable for healthcare applications. It integrates ESP modules and a Python Flask server, with open-source resources available on GitHub.
Runner-Up Prize Winners
- PCOSgen: This project compiles a predictive database for PCOS phenotypes, aiding early diagnosis and personalized treatment. It uses data-driven methodologies to address research gaps and improve patient outcomes.
Most Innovative Project Prize Winners
- Silent Witness: Graph-Based Abuse Detection: This initiative uses AI to analyze facial expressions from camera feeds to detect abuse patterns. By employing YOLO models for privacy, it constructs interaction graphs to identify and flag negative patterns while fostering positive environments.
For an extensive list of all participating projects, visit Watson Code Fest's project page.
About the Organizer
Kathmandu University Biotechnology Creatives
Kathmandu University Biotechnology Creatives (KUBiC) is a pioneering organization in biotechnology and bioinformatics. Known for hosting the annual Watson Code Fest, KUBiC serves as a platform for innovators, programmers, and creative thinkers to tackle crucial challenges in these fields. With a strong commitment to advancing biological sciences, KUBiC excels in fostering collaboration and creativity. Their mission is to redefine the future of biology and drive progress across interdisciplinary domains. More information can be found on their website.
-
 @ f9c0ea75:44e849f4
2025-01-12 20:47:48
@ f9c0ea75:44e849f4
2025-01-12 20:47:48For decades, Silicon Valley has been synonymous with innovation, and Wall Street has been the epicenter of economic power. Together, they shaped the modern world, attracting the brightest minds from top universities. Graduates once dreamed of launching startups, landing venture capital (VC) deals, or securing prestigious jobs in finance, believing that these industries were the engines of progress.
But as we enter 2025, the cracks in these once-revered institutions are undeniable. Silicon Valley and Wall Street, rather than pushing the boundaries of technological and financial evolution, have become disconnected from reality.
The truth is, these industries have not "exited the matrix." They have become prisoners of their own speculative cycles, artificial monetary systems, and short-term financial engineering. They thrive on hype and illusion rather than building anything of real value for society. And perhaps most significantly, they continue to dismiss Bitcoin—the one innovation that directly challenges the fiat-based foundation they stand on.
The Rise: From Innovation to Speculation
For much of the 20th and early 21st centuries, technology and finance were forces of real change.
- The 1980s–1990s: The rise of personal computing, the internet, and Wall Street’s financial expansion created unprecedented opportunities.
- The 2000s: The dot-com bubble burst but was followed by Web 2.0, mobile computing, and a boom in financial derivatives—setting the stage for the 2008 financial crisis.
- The 2010s: Silicon Valley reached peak influence with AI, social media, cloud computing, and the gig economy. Meanwhile, central banks printed trillions to "save" the economy, further detaching financial markets from real-world productivity.
Fast forward to today, and it's clear that both industries have lost their way.
The Fall: The Great Disconnection from Reality
### \ 1. Short-Term Thinking Over Long-Term Value
\ Silicon Valley claims to be about innovation, but today, it's mostly about speculation. Startups chase VC funding, aiming for rapid growth and an IPO rather than sustainable business models.
The problem extends to public companies as well. Stock buybacks, manipulated earnings reports, and short-term profit incentives dominate decision-making, sidelining real technological advancements.
2. The Financialization of Everything
\ The financial industry is no longer about allocating capital efficiently—it's about maximizing short-term gains. Markets are driven by quantitative trading algorithms, leveraged positions, and central bank policies rather than real economic fundamentals.
Silicon Valley has followed suit. Companies no longer prioritize profits but rather "growth metrics" to justify higher valuations. Business models rely on cheap debt and endless capital injections, creating an illusion of stability.
3. The Fiat Mentality: Creating Illusions Instead of Value
\ Both tech and finance have embraced a "fiat mentality"—the idea that value can be manufactured without real-world backing.
This is evident in:
- The NFT and crypto hype cycles, where billions are funneled into digital assets with no inherent utility.
- Silicon Valley startups burning cash endlessly, propped up by speculative VC money rather than genuine market demand.
- Financial markets defying economic fundamentals, rising even as debt levels skyrocket and productivity stagnates.
The collapse of Silicon Valley Bank (SVB) in 2023 was a warning. The bank failed because it operated on the assumption that interest rates would remain low forever. The industry ignored economic fundamentals, choosing instead to bet on infinite liquidity.
Yet, rather than acknowledging the flaws in the system, the response was predictable: more bailouts, more money printing, more denial.
The Industry’s Biggest Blind Spot: Bitcoin
If there’s one thing that exposes the flaws of the modern financial and tech industries, it’s Bitcoin. And yet, Silicon Valley and Wall Street continue to misunderstand it.
1. They Confuse Bitcoin with "Crypto"
Silicon Valley lumps Bitcoin into the same category as speculative crypto tokens, meme coins, and NFT projects. They fail to see that Bitcoin is fundamentally different—it is decentralized, permissionless, and operates on a fixed monetary supply, unlike fiat currencies or VC-backed blockchain projects.
2. They Underestimate Its Monetary Revolution Finance
professionals dismiss Bitcoin because they are too invested in the fiat system. The very institutions that dominate global finance—central banks, commercial banks, and hedge funds—are threatened by a monetary system that operates outside their control.
Bitcoin is not just another asset; it is a paradigm shift. It removes reliance on central banks, eliminates counterparty risk, and offers financial sovereignty in a world where fiat currencies are continuously debased.
3. They Ignore the Reality of the Debt-Driven System
The global economy runs on an unsustainable debt-based model. Governments and corporations rely on constant money printing to sustain growth, leading to asset bubbles and financial instability. Bitcoin exposes this because it operates on absolute scarcity—there will only ever be 21 million Bitcoin.
Wall Street and Silicon Valley refuse to acknowledge this reality because doing so would force them to confront the weaknesses of their own industries.
Bitcoin and the Exit from the Matrix
The industries that once defined the future—tech and finance—have ironically failed to recognize the most important technological advancement of our time. They are too focused on short-term profits and centralized control to understand that the future of money will not be dictated by governments or banks—it will be dictated by individuals choosing financial independence.
Silicon Valley and Wall Street have built an empire based on leverage, speculation, and centralization. But history has shown that these systems eventually collapse under their own weight.
The question is: Who will wake up in time?
The Future Belongs to Those Who See the Shift
The Silicon Valley and Wall Street elites have not exited the matrix. They remain trapped in a system that prioritizes financial illusions over real value.
But history does not wait for those unwilling to adapt.
-
 @ 16d11430:61640947
2025-01-20 03:17:38
@ 16d11430:61640947
2025-01-20 03:17:38Born out of a silent rage into a world that prides itself on polished veneers of socially acceptable fury, the Silent Rager arrived in a place where anger wore masks—tight, suffocating masks that twisted raw emotion into hollow smiles and passive-aggressive jabs. Yet his rage had no such mask, no place in this theater of deceit. His was a wild, untamed thing, a fire roaring without the permission of his voice.
From the moment he could perceive the world, he was sent to rage's hell camp—a crucible of misery, where every breath reeked of malfeasance, and every lesson was soaked in contempt. The Silent Rager learned to stew in it, learned to hold it within, to cook himself in the boiling broth of inherited bitterness and unspoken injustice. They told him the world was cruel, but what they didn’t tell him was that he’d been chosen—culled in a ritual as old as power itself. Somewhere, someone had decided that his voice was too dangerous to exist. They’d silenced it before it could ever cry out, sparing the rage but not the sound.
And so, he grew, misinformed, misdirected, and malformed. His mind writhed like a worm trapped in the grip of an unseen hand. Thoughts coiled and uncoiled in his brain, each one dripping with questions he could not articulate, answers he could not demand. Why was his rage silent? Why did it claw at his chest without release? He did not know. He only knew the ache of containment and the suffocating weight of emotions too vast for his stolen voice.
Moments of respite came, but only when he danced closest to death. The edge of oblivion whispered to him with the intimacy of a long-lost friend. It was in these moments that the raging fire within dimmed, replaced by a fleeting, fragile stillness. He could breathe, if only for a second, before the storm returned. Life, for him, was not a series of triumphs or failures but a relentless march of inherited rage, coursing through his veins like a parasite, feeding on his every heartbeat.
He did not ache for it to end—not entirely. What he yearned for, more than anything, was a voice. A voice to scream into the void that birthed him. A voice to challenge the silence that caged him. A voice to tell the world, and himself, the truth of his existence before he could end it all.
The Silent Rager lived in a paradox: to end his life without a voice would be to die unseen, unheard, unspoken. But to live on without one felt equally unbearable. His rage, silent though it was, demanded expression. It screamed through his actions, burned in his gaze, and radiated from him like heat from a furnace. And yet, the world did not see, did not hear. To them, he was just another shadow moving through the crowd, another ghost in the machine.
In the end, the Silent Rager remained trapped in his silent storm, his unvoiced agony a testament to a life stolen before it could begin. Perhaps one day he would find his voice. Or perhaps his silence would be his epitaph, a bitter monument to a world that let him burn in quiet desperation. Until then, he raged—silent, but not unseen, not by those who dared to truly look.
-
 @ 16d11430:61640947
2025-01-19 22:19:00
@ 16d11430:61640947
2025-01-19 22:19:00Welcome, intrepid traveler, to the uncharted territory of the mind! This guide draws from the greatest explorers, philosophers, and scientists who dared to map the mysteries of inner space. Pack your curiosity, buckle up, and prepare for a journey through the vast landscapes of consciousness, perception, and human potential.
Chapter 1: Know Thy Mind (Before It Knows You)
Key References: "Incognito" by David Eagleman, "The Power of Now" by Eckhart Tolle
The first rule of mind travel: most of what happens in your brain is unconscious. Your mind is like an iceberg—only the tip is visible (your conscious thoughts). Beneath lies a vast network of automatic processes shaping your perceptions and decisions.
Tips for Hitchhikers:
Pause and Observe: Cultivate mindfulness to slow the chatter of the conscious mind and observe the silent work of the subconscious.
Live in the Now: As Tolle advises, consciousness thrives in the present. The past is a memory, and the future is a projection—neither exists outside your mind.
Chapter 2: The Art of Inner Travel
Key References: "The Mind Illuminated" by John Yates, "The Doors of Perception" by Aldous Huxley
Traveling inward requires tools, and meditation is the universal passport. It trains your attention, opens doors to altered states of awareness, and reveals the boundless nature of your mind.
Tips for Hitchhikers:
Follow the Breath: Start simple. Focus on the rhythm of your breathing. This anchors you to the present and quiets mental noise.
Explore Altered States: As Huxley discovered, substances like psychedelics (when used responsibly) or profound meditation can dissolve mental barriers, revealing the infinite.
Chapter 3: Habitual Programming
Key References: "Atomic Habits" by James Clear, "Superhuman by Habit" by Tynan
Your mind is a creature of habit. Over time, these habits carve neural pathways, shaping your behavior. The good news? You can rewrite these programs.
Tips for Hitchhikers:
Small Changes, Big Impact: Focus on small, consistent habits. Tiny tweaks lead to massive shifts in your mental landscape.
Hack Feedback Loops: Celebrate victories and reflect on failures. Every action trains your brain for future behavior.
Chapter 4: The Flow State – Consciousness on Turbo Drive
Key References: "Stealing Fire" by Steven Kotler, "The Inner Game of Tennis" by W. Timothy Gallwey
Flow is the ultimate ride—effortless, joyful immersion where you lose yourself in the task. It’s the mind’s cheat code for peak performance and creativity.
Tips for Hitchhikers:
Find the Edge: Engage in activities slightly beyond your skill level. Flow lives in the challenge.
Eliminate Distractions: Turn off notifications, declutter your space, and give your full attention to the task.
Chapter 5: Neuroplasticity – Rewiring the Inner Highway
Key References: "The Brain That Changes Itself" by Norman Doidge
Your brain is not static; it’s a living, evolving organ capable of change. Neuroplasticity means that thoughts and actions can reshape your mental circuitry.
Tips for Hitchhikers:
Practice Makes Permanent: Repetition strengthens neural connections. What you focus on grows stronger.
Challenge the Mind: Learn a new skill, speak a new language, or solve puzzles to keep your brain adaptable.
Chapter 6: Consciousness and the Cosmos
Key References: "Zen and the Art of Motorcycle Maintenance" by Robert M. Pirsig, "Dune" by Frank Herbert
Consciousness doesn’t exist in isolation—it’s a dance with the external world. Whether through Zen-like awareness or understanding the interconnectedness of all things, your journey is both inward and outward.
Tips for Hitchhikers:
Seek Quality: Pirsig describes quality as the intersection of science and art. Find meaning in the smallest details.
Embrace Interdependence: Like Herbert’s vision in Dune, see yourself as part of a larger system, from the microscopic to the cosmic.
Chapter 7: Altered Perception – The Mind's Infinite Dimensions
Key References: "VALIS" by Philip K. Dick, "How to Change Your Mind" by Michael Pollan
Reality is what your brain perceives it to be, but perception can be altered. Explore, but tread carefully.
Tips for Hitchhikers:
Question Reality: Ask yourself: Is what I perceive objective truth or the brain’s best guess?
Expand Carefully: Use Pollan’s guide for safe and structured exploration of altered states.
Chapter 8: Superconsciousness – Becoming More Than You Are
Key References: "Becoming Supernatural" by Dr. Joe Dispenza
The ultimate destination for hitchhikers is unlocking the superconscious—a state where you transcend your limitations and become the architect of your reality.
Tips for Hitchhikers:
Visualization: Envision the future you desire. Your brain rewires itself to make this vision a reality.
Heart-Brain Coherence: Sync emotional and mental states for profound inner balance.
Final Thoughts: Don't Panic (and Keep Exploring!)
Consciousness is the greatest mystery of the universe—complex, vast, and thrilling. Treat every moment as an opportunity for growth and self-discovery. The Hitchhiker’s Guide to Consciousness doesn’t offer all the answers, but it does remind you to keep asking the right questions.
And remember: the mind is infinite, and so are you. Safe travels, fellow hitchhiker!
-
 @ f9cf4e94:96abc355
2024-12-31 20:18:59
@ f9cf4e94:96abc355
2024-12-31 20:18:59Scuttlebutt foi iniciado em maio de 2014 por Dominic Tarr ( dominictarr ) como uma rede social alternativa off-line, primeiro para convidados, que permite aos usuários obter controle total de seus dados e privacidade. Secure Scuttlebutt (ssb) foi lançado pouco depois, o que coloca a privacidade em primeiro plano com mais recursos de criptografia.
Se você está se perguntando de onde diabos veio o nome Scuttlebutt:
Este termo do século 19 para uma fofoca vem do Scuttlebutt náutico: “um barril de água mantido no convés, com um buraco para uma xícara”. A gíria náutica vai desde o hábito dos marinheiros de se reunir pelo boato até a fofoca, semelhante à fofoca do bebedouro.

Marinheiros se reunindo em torno da rixa. ( fonte )
Dominic descobriu o termo boato em um artigo de pesquisa que leu.
Em sistemas distribuídos, fofocar é um processo de retransmissão de mensagens ponto a ponto; as mensagens são disseminadas de forma análoga ao “boca a boca”.
Secure Scuttlebutt é um banco de dados de feeds imutáveis apenas para acréscimos, otimizado para replicação eficiente para protocolos ponto a ponto. Cada usuário tem um log imutável somente para acréscimos no qual eles podem gravar. Eles gravam no log assinando mensagens com sua chave privada. Pense em um feed de usuário como seu próprio diário de bordo, como um diário de bordo (ou diário do capitão para os fãs de Star Trek), onde eles são os únicos autorizados a escrever nele, mas têm a capacidade de permitir que outros amigos ou colegas leiam ao seu diário de bordo, se assim o desejarem.
Cada mensagem possui um número de sequência e a mensagem também deve fazer referência à mensagem anterior por seu ID. O ID é um hash da mensagem e da assinatura. A estrutura de dados é semelhante à de uma lista vinculada. É essencialmente um log somente de acréscimo de JSON assinado. Cada item adicionado a um log do usuário é chamado de mensagem.
Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.

Perspectivas dos participantes
Scuttlebot
O software Pub é conhecido como servidor Scuttlebutt (servidor ssb ), mas também é conhecido como “Scuttlebot” e
sbotna linha de comando. O servidor SSB adiciona comportamento de rede ao banco de dados Scuttlebutt (SSB). Estaremos usando o Scuttlebot ao longo deste tutorial.Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.


Perspectivas dos participantes
Pubs - Hubs
Pubs públicos
| Pub Name | Operator | Invite Code | | ------------------------------------------------------------ | ------------------------------------------------------------ | ------------------------------------------------------------ | |
scuttle.us| @Ryan |scuttle.us:8008:@WqcuCOIpLtXFRw/9vOAQJti8avTZ9vxT9rKrPo8qG6o=.ed25519~/ZUi9Chpl0g1kuWSrmehq2EwMQeV0Pd+8xw8XhWuhLE=| | pub1.upsocial.com | @freedomrules |pub1.upsocial.com:8008:@gjlNF5Cyw3OKZxEoEpsVhT5Xv3HZutVfKBppmu42MkI=.ed25519~lMd6f4nnmBZEZSavAl4uahl+feajLUGqu8s2qdoTLi8=| | Monero Pub | @Denis |xmr-pub.net:8008:@5hTpvduvbDyMLN2IdzDKa7nx7PSem9co3RsOmZoyyCM=.ed25519~vQU+r2HUd6JxPENSinUWdfqrJLlOqXiCbzHoML9iVN4=| | FreeSocial | @Jarland |pub.freesocial.co:8008:@ofYKOy2p9wsaxV73GqgOyh6C6nRGFM5FyciQyxwBd6A=.ed25519~ye9Z808S3KPQsV0MWr1HL0/Sh8boSEwW+ZK+8x85u9w=| |ssb.vpn.net.br| @coffeverton |ssb.vpn.net.br:8008:@ze8nZPcf4sbdULvknEFOCbVZtdp7VRsB95nhNw6/2YQ=.ed25519~D0blTolH3YoTwSAkY5xhNw8jAOjgoNXL/+8ZClzr0io=| | gossip.noisebridge.info | Noisebridge Hackerspace @james.network |gossip.noisebridge.info:8008:@2NANnQVdsoqk0XPiJG2oMZqaEpTeoGrxOHJkLIqs7eY=.ed25519~JWTC6+rPYPW5b5zCion0gqjcJs35h6JKpUrQoAKWgJ4=|Pubs privados
Você precisará entrar em contato com os proprietários desses bares para receber um convite.
| Pub Name | Operator | Contact | | --------------------------------------------- | ------------------------------------------------------------ | ----------------------------------------------- | |
many.butt.nz| @dinosaur | mikey@enspiral.com | |one.butt.nz| @dinosaur | mikey@enspiral.com | |ssb.mikey.nz| @dinosaur | mikey@enspiral.com | | ssb.celehner.com | @cel | cel@celehner.com |Pubs muito grandes
Aviso: embora tecnicamente funcione usar um convite para esses pubs, você provavelmente se divertirá se o fizer devido ao seu tamanho (muitas coisas para baixar, risco para bots / spammers / idiotas)
| Pub Name | Operator | Invite Code | | --------------------------------------- | ----------------------------------------------- | ------------------------------------------------------------ | |
scuttlebutt.de| SolSoCoG |scuttlebutt.de:8008:@yeh/GKxlfhlYXSdgU7CRLxm58GC42za3tDuC4NJld/k=.ed25519~iyaCpZ0co863K9aF+b7j8BnnHfwY65dGeX6Dh2nXs3c=| |Lohn's Pub| @lohn |p.lohn.in:8018:@LohnKVll9HdLI3AndEc4zwGtfdF/J7xC7PW9B/JpI4U=.ed25519~z3m4ttJdI4InHkCtchxTu26kKqOfKk4woBb1TtPeA/s=| | Scuttle Space | @guil-dot | Visit scuttle.space | |SSB PeerNet US-East| timjrobinson |us-east.ssbpeer.net:8008:@sTO03jpVivj65BEAJMhlwtHXsWdLd9fLwyKAT1qAkc0=.ed25519~sXFc5taUA7dpGTJITZVDCRy2A9jmkVttsr107+ufInU=| | Hermies | s | net:hermies.club:8008~shs:uMYDVPuEKftL4SzpRGVyQxLdyPkOiX7njit7+qT/7IQ=:SSB+Room+PSK3TLYC2T86EHQCUHBUHASCASE18JBV24= |GUI - Interface Gráfica do Utilizador(Usuário)
Patchwork - Uma GUI SSB (Descontinuado)
Patchwork é o aplicativo de mensagens e compartilhamento descentralizado construído em cima do SSB . O protocolo scuttlebutt em si não mantém um conjunto de feeds nos quais um usuário está interessado, então um cliente é necessário para manter uma lista de feeds de pares em que seu respectivo usuário está interessado e seguindo.

Fonte: scuttlebutt.nz
Quando você instala e executa o Patchwork, você só pode ver e se comunicar com seus pares em sua rede local. Para acessar fora de sua LAN, você precisa se conectar a um Pub. Um pub é apenas para convidados e eles retransmitem mensagens entre você e seus pares fora de sua LAN e entre outros Pubs.
Lembre-se de que você precisa seguir alguém para receber mensagens dessa pessoa. Isso reduz o envio de mensagens de spam para os usuários. Os usuários só veem as respostas das pessoas que seguem. Os dados são sincronizados no disco para funcionar offline, mas podem ser sincronizados diretamente com os pares na sua LAN por wi-fi ou bluetooth.
Patchbay - Uma GUI Alternativa
Patchbay é um cliente de fofoca projetado para ser fácil de modificar e estender. Ele usa o mesmo banco de dados que Patchwork e Patchfoo , então você pode facilmente dar uma volta com sua identidade existente.

Planetary - GUI para IOS

Planetary é um app com pubs pré-carregados para facilitar integração.
Manyverse - GUI para Android

Manyverse é um aplicativo de rede social com recursos que você esperaria: posts, curtidas, perfis, mensagens privadas, etc. Mas não está sendo executado na nuvem de propriedade de uma empresa, em vez disso, as postagens de seus amigos e todos os seus dados sociais vivem inteiramente em seu telefone .
Fontes
-
https://scuttlebot.io/
-
https://decentralized-id.com/decentralized-web/scuttlebot/#plugins
-
https://medium.com/@miguelmota/getting-started-with-secure-scuttlebut-e6b7d4c5ecfd
-
Secure Scuttlebutt : um protocolo de banco de dados global.
-
-
 @ 75869cfa:76819987
2025-01-20 06:22:49
@ 75869cfa:76819987
2025-01-20 06:22:49GM, Nostriches! The Nostr Review is a biweekly newsletter focused on Nostr statistics, protocol updates, exciting programs, the long-form content ecosystem, and key events happening in the Nostr-verse. If you’re interested, join me in covering updates from the Nostr ecosystem!
Quick review: In the past two weeks, Nostr statistics indicate over 224,000 daily trusted pubkey events.The number of new users has seen a significant increase. Profiles with contact list amount is four times the amount from the same period. Public writing events have reflected a 50% increase. More than 9 million events have been published, with posts leading in volume at around 1.3 million, representing a significant 32% decrease. Total Zap activity stands at approximately 9 million, marking a 20% decline.
Additionally, 16 pull requests were submitted to the Nostr protocol, with 8 merged. A total of 45 Nostr projects were tracked, with 13 releasing product updates, and over 337 long-form articles were published, 34% focusing on Bitcoin and Nostr. During this period, 1 notable event took place, and 3 significant events are upcoming.
Nostr Statistics
Based on user activity, the total daily trusted pubkeys writing events is about 224,000, representing a slight 5.5% decrease compared to the previous period (8-22 Dec). Daily activity peaked at 18053 events, with a low of approximately 16276.
The number of new users has seen a significant increase. Profiles with contact list amount to approximately 18,340, which is four times the amount from the same period. Pubkeys writing events total around 80,000, reflecting a 50% increase compared to the same period.
Regarding event publishing, the total number of note events published is about 9 million, marking an increase of above 20%.Posts remain the most dominant in terms of volume, totaling approximately 1.3 million, reflecting a notable decrease of 32%. Reposts stand at around 327,000, showing a decline of approximately 8.5%, while reactions have experienced a significant increase, rising by 18% to reach 635,012.
For zap activity, the total zap amount is about 9 million, showing a decrease of over 20% compared to the previous period.
In terms of relay usage, the top five relays by user count are: wss://bostr.bitcointxoko.com/, wss://feeds.nostr.band/, wss://relays.diggoo.com/, wss://bostr.azzamo.net/, wss://bostr.lightningspore.com/
Data source: https://stats.nostr.band/
NIPs
Asset prices nostr:npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z defines event kinds to host asset prices.Kind 31892 stores the latest conversion price. The d tag contains the commonly used ticket conversion symbol for the pair. The value tag contains the amount, parseable to a Decimal. n tags separate the pair into the two ticket symbols. The event's created_at field MUST be used as the date/time of the conversion value.Kind 10041 lists the user's authorized providers for pricing services. It contains s tags with the provider's pubkey and the relay where those events are stored.
nip-38: chained stories. Kehiy defines a new status type which lets users share a chain of stories.This NIP enables a way for users to share live statuses such as what music they are listening to, as well as what they are currently doing: work, play, out of office, etc. A special event with kind:30315 “User Status” is defined as an optionally expiring addressable event, where the d tag represents the status type.The status MAY include an r, p, location, e or a tag linking to a URL, profile, location, note, or addressable event. The content MAY include emoji(s), or NIP-30 custom emoji(s). If the content is an empty string then the client should clear the status.Clients MAY display this next to the username on posts or profiles to provide live user status information.
adding x tag to nip56 Kehiy is proposing that with the growth of clients like zap stream, olas, chat apps, or music clients we have more stuff that may need to be reported. here we can support blobs. When Nostr grows in using media based clients, like zap.stream or olas or music clients, then the event itself is not too important and the media is more important. by reporting events, the media is still accessible. We can support reports ol medias like this.
NIP-91: Extension Negotiation Semisol is proposing that NIP-91 adds an extension negotiation scheme for clients and relays to negotiate new protocols. The intended goal is to replace NIP-11 for the discovery of relay supported features. An extension feature negotiation scheme is also included.
Trusting rumors by entirely trusted relay list nanikamado has decided to require Nostr users to register their pubkeys to access the bridge after discussions with some Fediverse users. Unregistered users will be denied both read and write access, operating similarly to a paid relay. In addition, measures will be implemented to prevent events within the bridge relay from being broadcast to other relays, even if it compromises compatibility. The "-" tag alone is insufficient for this requirement. This NIP has already been implemented on the relay: nanikamado/rockstr@f968149. There are also plans to fork a web client and implement this NIP there.
Notable Projects
Amethyst v0.94.3 nostr:npub142gywvjkq0dv6nupggyn2euhx4nduwc7yz5f24ah9rpmunr2s39se3xrj0 * Adds iMeta tags to GIF urls * Adds iMeta tags to GIF urls to optimize GIF previews * Fixes the extra empty kind 20 post when uploading videos on the media tab * Fix: Only close the upload screen if the video upload is a success on the Media tab * Maintains note reaction visibility when scrolling by nostr:npub1xcl47srtwh4klqd892s6fzwtdfm4y03wzjfl78scmmmxg8wzsf4qftd0en
Flotilla 0.2.1 nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn * Improve performance, as well as scrolling and loading * Integrate * Improve NIP 29 compatibility * Fix incorrect connection errors * Refine notifications * Add room menu to space homepage * Fix storage bugs * Add join space CTA
Primal for Android build 2.0.34 nostr:npub12vkcxr0luzwp8e673v29eqjhrr7p9vqq8asav85swaepclllj09sylpugg They now support the full highlighting feature set for long form notes: highlight display, select any text & highlight, comment on highlights, share highlights in your main feed. They also added btc/usd conversions in the wallet, as well as other small fixes and improvements.
0xchat App v1.4.5 & Desktop v1.0.1 nostr:npub1tm99pgz2lth724jeld6gzz6zv48zy6xp4n9xu5uqrwvx9km54qaqkkxn72 * Added support for NIP46 login. * Adapted UI for tablet devices. * Introduced connection ping status. * Implemented search functionality for Moments. * Set default relays for first login. * Added default reaction emojis. * Fixed an issue where messages couldn't be sent after joining a relay group. * Resolved occasional UI flipping issues. * Fixed an issue preventing images from being moved after zooming. * Addressed a bug causing voice messages to get stuck in a loading state. * Fixed file encryption and decryption issues. * Corrected some typos. * Fixed an issue with Nostr.build uploads.
Yakihonne Latest Update (iOS/Android/Web/Zap.Store) nostr:npub1yzvxlwp7wawed5vgefwfmugvumtp8c8t0etk3g8sky4n0ndvyxesnxrf8q
Web: * Yakihonne is now multilingual! Enjoy the app in English and Chinese, with more languages coming soon, including Spanish, Portuguese, Thai, Arabic, Japanese, and Italian. * Added support for translating notes and articles into the app's selected language. * Copy-paste images to upload seamlessly across the app. * Resolved issues with secure DMs when logging in using a private key. * General bug fixes and improvements. * Article drafts now can be cleared directly or the published one will no more be existed
Mobile: * App languages: Yakihonne is now multilingual! Enjoy the app in English and Chinese, with more languages coming soon, including Spanish, Portuguese, Thai, Arabic, Japanese, and Italian. * Translation: Added support for translating notes and articles into the app's selected language. * Wallet balance: Fix issue where wallet balance is N/A. * Account initialization: Fix issue when initializing account. * Paying invoice: Fix issue sending sats using invoices.
Olas 0.1.7.1 nostr:npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft * Works with remote signers like Amber (on nsecbunker mode). * The video tab now plays short videos with sound on and stops playing when you swipe out * Yet even more performance improvements * Fixed a bug where Android wasn't calculating blurhashes * Always adds image dimensions when posting so @Vitor Pamplona is happier. * “Some” fixes on NWC wallets, but it's still quite buggy, will investigate more -- if you've received zaps on your Olas posts today, that was probably me zapping via NWC + remote signing those zaps.
Wherostr v1.3.3 nostr:npub16elg3wf8nffkymylw9kfwecc45j9c30lufrrzx2zf5vmxjlcgkkq3xc6d7 * File Upload Error: Resolved the “404 Not Found” issue during file uploads. * Increased Geohash Precision: Enhanced location accuracy by increasing geohash precision from 9 to 11.
DEG Mods nostr:npub17jl3ldd6305rnacvwvchx03snauqsg4nz8mruq0emj9thdpglr2sst825x * A small update went live: * A “try again” button appears on mods that error out. (99% of the time this fixes the issue). * The blog tab in a user's profile now loads correctly (doesn't get stuck anymore for new users) * Text now appears if a game isn't found in the search * Looking into fixing one newly discovered issue related to old mods * Easier media uploads (drag and drop basically. No need to go find other sites to upload images to anymore)
AlbyHub 1.11.4 nostr:npub1getal6ykt05fsz5nqu4uld09nfj3y3qxmv8crys4aeut53unfvlqr80nfm * You can use all the features of Alby Hub in self-custody with LND on Raspiblitz, now available in WebUI.
Zapstore 0.2.0 nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8 * 0.2.0 is out with support for signing in with Amber (NIP-55) and zaps via Nostr Wallet Connect.
Narr release v0.3.2 nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 * New Narr release v0.3.2 fixes all the problems with articles updating, insufficiently-rendered Markdown, Nostr usernames not loading, and makes everything better. * It supports all sorts of RSS feed discovery from HTTP URLs and renders them beautifully in a simple straightforward interface, you can also paste nostr:... URIs, including nip05, npub and nprofile codes (they should also work without the nostr: prefix).
ZEUS v0.9.4 nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5 * Embedded Node: LND v0.18.4 * Speed up tx UX improvements * CLNRest: display of destination addresses on txs * Display keysend messages in Activity + Payment views * Open Channel view: Connect Peer UI tabs * CLNRest: paste connection strings * Channels: sort by Close Height * Optimizations + bug fixes
Citrine 0.6.0 nostr:npub1hqlxlq57nvlq70ugmsmu9y5lmyc5k2lh5w7y85j7dgsr5u7zwavq5agspw * Update dependencies * Show notifications when importing, exporting, downloading events * Change database functions to be suspending functions
Long-Form Content Eco
In the past two weeks, more than 337 long-form articles have been published, including over 93 articles on Bitcoin and more than 22 related to Nostr, accounting for 34% of the total content.
These articles about Nostr mainly explore its diverse applications and potential impacts across various domains. Topics range from technical guides like creating custom emojis and automating workflows, to cultural and social aspects, such as the Nostr Bread Festival and the role of Nostr in enhancing free speech. There are reflections on the past year's developments, predictions for 2025, and discussions on integrating Nostr with other platforms like Bluesky. The content also delves into personal experiences, community interactions, and broader societal issues, highlighting Nostr's growing influence and the creative ways users are engaging with this decentralized network.
The Bitcoin articles discuss a wide range of topics, from technological innovations to socio-economic impacts. They cover the speed advantages of the Lightning Network, the economic model policies of Bitcoin, and the outlook for Bitcoin's development in 2024. Some articles analyze the relationship between Bitcoin and traditional financial markets like the Nikkei 225, highlighting the potential of a decentralized future and the spread of Bitcoin education. Additionally, they explore the possibility of Bitcoin as a legal tender, its connection to religious and spiritual dimensions, and the mystery surrounding Satoshi Nakamoto's identity. Reflections on Bitcoin's milestones, such as the release of the genesis block, emphasize its challenge and revolution to the modern financial system. Overall, these articles showcase Bitcoin's profound global impact and its continually evolving ecosystem.
Thankyou, nostr:npub1xr8tvnnnr9aqt9vv30vj4vreeq2mk38mlwe7khvhvmzjqlcghh6sr85uum nostr:npub1zmg3gvpasgp3zkgceg62yg8fyhqz9sy3dqt45kkwt60nkctyp9rs9wyppc nostr:npub15wplsmd8uqul4a5l55n9e6kcd5fcrgxvwa6jredncvdr8nd5zl2qswqcsn nostr:npub1a6g9g0a3rweu7jkujrgldlsrrjv42u070qmxxfv5axk0eymrg4ls0vll8d nostr:npub1dr8yfep5kezfcq5u9dhdulhcegknwlauqrlvfwjw7rkprmx4746qfxjj6h nostr:npub1fhl7c96k3vdv4ge8rv26cda4qyxnqd605x2w7l58euy0jnzvh4yq5hvm20 nostr:npub1tx0k0a7lw62vvqax6p3ku90tccgdka7ul4radews2wrdsg0m865szf9fw6 nostr:npub1tzfhjkqrdnk7j4djtwfftqupgzazm6kt35vnnmv35sd7y4z7dx2qzhkje9 and others, for your work. Enriching Nostr’s long-form content ecosystem is crucial.
Nostriches Global Meet Ups
Recently, a Nostr event have been hosted. * The Bitcoin Meetup took place on December 29, 2024, at the “Accra City Pub” in Jamestown. The event featured the “Orange Pilling” session at 3:00 PM, followed by the GH Bitcoin NYTZ meetup at 7:00 PM. Participants also had the chance to win a free Trezor Safe 3 hardware wallet, and the event was free to attend.
Here are the upcoming Nostr events in November that you might want to check out.
-
The Bitcoin City Team Hackathon will take place online (via Discord) from January 10 to January 31, 2025. This event aims to develop a fun and interactive visualization of live Bitcoin and Lightning transactions. Participating teams will have the opportunity to win a total prize of 10,000,000 IDR. nostr:npub1y4qd2zhtn05gnsaaq5xfejzfk4a32638tx6gpp9g8k6e42g9d66qaxhcr3
-
The inaugural Bitcoin Circular Economy Summit will be held from January 27th to 29th in El Zonte, El Salvador! This three-day event includes leadership training, Bitcoin education, and exchanges with over 15 global Bitcoin circular economies. It offers a unique opportunity for global leaders in Bitcoin adoption and economic development to connect, learn, and collaborate. This summit precedes the PlanB Forum, taking place on January 30th-31st in San Salvador, making it an excellent chance to network with Bitcoin users worldwide.
-
The Bitcoin Freedom Festival will take place from February 20 to 24, 2025, at the Awakening Center in Uvita, Costa Rica. In collaboration with the Awake Earth Festival, this event blends a music festival with Bitcoin seminars and lectures. From February 20 to 23, the focus will be on music, healing workshops, ceremonies, and educational talks, featuring internationally renowned artists and captivating discussions. February 24 will be a special day dedicated to Bitcoin, with all activities centered around it. nostr:npub14f26g7dddy6dpltc70da3pg4e5w2p4apzzqjuugnsr2ema6e3y6s2xv7lu
Additionally, We warmly invite event organizers who have held recent activities to reach out to us so we can work together to promote the prosperity and development of the Nostr ecosystem.
Thanks for reading! If there’s anything I missed, feel free to reach out and help improve the completeness and accuracy of my coverage.
-
-
 @ 266815e0:6cd408a5
2024-04-22 22:20:47
@ 266815e0:6cd408a5
2024-04-22 22:20:47While I was in Mediera with all the other awesome people at the first SEC cohort there where a lot of discussions around data storage on nostr and if it could be made censorship-resistent
I remember lots of discussions about torrents, hypercore, nostr relays, and of course IPFS
There were a few things I learned from all these conversations:
- All the existing solutions have one thing in common. A universal ID of some kind for files
- HTTP is still good. we don't have to throw the baby out with the bath water
- nostr could fix this... somehow
Some of the existing solutions work well for large files, and all of them are decentralization in some way. However none of them seem capable of serving up cat pictures for social media clients. they all have something missing...
An Identity system
An identity system would allow files to be "owned" by users. and once files have owners servers could start grouping files into a single thing instead of a 1000+ loose files
This can also greatly simplify the question of "what is spam" for a server hosting (or seeding) these files. since it could simply have a whitelist of owners (and maybe their friends)
What is blossom?
Blossom is a set of HTTP endpoints that allow nostr users to store and retrieve binary data on public servers using the sha256 hash as a universal id
What are Blobs?
blobs are chunks of binary data. they are similar to files but with one key difference, they don't have names
Instead blobs have a sha256 hash (like
b1674191a88ec5cdd733e4240a81803105dc412d6c6708d53ab94fc248f4f553) as an IDThese IDs are universal since they can be computed from the file itself using the sha256 hashing algorithm ( you can get a files sha256 hash on linux using:
sha256sum bitcoin.pdf)How do the servers work?
Blossom servers expose four endpoints to let clients and users upload and manage blobs
GET /<sha256>(optional file.ext)PUT /uploadAuthentication: Signed nostr event- Returns a blob descriptor
GET /list/<pubkey>- Returns an array of blob descriptors
Authentication(optional): Signed nostr eventDELETE /<sha256>Authentication: Signed nostr event
What is Blossom Drive?
Blossom Drive is a nostr app built on top of blossom servers and allows users to create and manage folders of blobs
What are Drives
Drives are just nostr events (kind
30563) that store a map of blobs and what filename they should have along with some extra metadataAn example drive event would be
json { "pubkey": "266815e0c9210dfa324c6cba3573b14bee49da4209a9456f9484e5106cd408a5", "created_at": 1710773987, "content": "", "kind": 30563, "tags": [ [ "name", "Emojis" ], [ "description", "nostr emojis" ], [ "d", "emojis" ], [ "r", "https://cdn.hzrd149.com/" ], [ "x", "303f018e613f29e3e43264529903b7c8c84debbd475f89368cb293ec23938981", "/noStrudel.png", "15161", "image/png" ], [ "x", "a0e2b39975c8da1702374b3eed6f4c6c7333e6ae0008dadafe93bd34bfb2ca78", "/satellite.png", "6853", "image/png" ], [ "x", "e8f3fae0f4a43a88eae235a8b79794d72e8f14b0e103a0fed1e073d8fb53d51f", "/amethyst.png", "20487", "image/png" ], [ "x", "70bd5836807b916d79e9c4e67e8b07e3e3b53f4acbb95c7521b11039a3c975c6", "/nos.png", "36521", "image/png" ], [ "x", "0fc304630279e0c5ab2da9c2769e3a3178c47b8609b447a30916244e89abbc52", "/primal.png", "29343", "image/png" ], [ "x", "9a03824a73d4af192d893329bbc04cd3798542ee87af15051aaf9376b74b25d4", "/coracle.png", "18300", "image/png" ], [ "x", "accdc0cdc048f4719bb5e1da4ff4c6ffc1a4dbb7cf3afbd19b86940c01111568", "/iris.png", "24070", "image/png" ], [ "x", "2e740f2514d6188e350d95cf4756bbf455d2f95e6a09bc64e94f5031bc4bba8f", "/damus.png", "32758", "image/png" ], [ "x", "2e019f08da0c75fb9c40d81947e511c8f0554763bffb6d23a7b9b8c9e8c84abb", "/old emojis/astral.png", "29365", "image/png" ], [ "x", "d97f842f2511ce0491fe0de208c6135b762f494a48da59926ce15acfdb6ac17e", "/other/rabbit.png", "19803", "image/png" ], [ "x", "72cb99b689b4cfe1a9fb6937f779f3f9c65094bf0e6ac72a8f8261efa96653f5", "/blossom.png", "4393", "image/png" ] ] }There is a lot going on but the main thing is the list of "x" tags and the path that describes the folder and filename the blob should live at
If your interested, the full event definition is at github.com/hzrd149/blossom-drive
Getting started
Like every good nostr client it takes a small instruction manual in order to use it properly. so here are the steps for getting started
1. Open the app
Open https://blossom.hzrd149.com
2. Login using extension

You can also login using any of the following methods using the input - NIP-46 with your https://nsec.app or https://flare.pub account - a NIP-46 connection string - an
ncryptsecpassword protected private key - ansecunprotected private key (please don't) - bunker:// URI from nsecbunker3. Add a blossom server

Right now
https://cdn.satellite.earthis the only public server that is compatible with blossom drive. If you want to host your own I've written a basic implementation in TypeScript github.com/hzrd149/blossom-server4. Start uploading your files
NOTE: All files upload to blossom drive are public by default. DO NOT upload private files

5. Manage files

Encrypted drives
There is also the option to encrypt drives using NIP-49 password encryption. although its not tested at all so don't trust it, verify

Whats next?
I don't know, but Im excited to see what everyone else on nostr builds with this. I'm only one developer at the end of the day and I can't think of everything
also all the images in this article are stored in one of my blossom drives here
nostr:naddr1qvzqqqrhvvpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qq8xzun5d93kcefdd9kkzem9wvr46jka
-
 @ f977c464:32fcbe00
2024-01-30 20:06:18
@ f977c464:32fcbe00
2024-01-30 20:06:18Güneşin kaybolmasının üçüncü günü, saat öğlen on ikiyi yirmi geçiyordu. Trenin kalkmasına yaklaşık iki saat vardı. Hepimiz perondaydık. Valizlerimiz, kolilerimiz, renk renk ve biçimsiz çantalarımızla yan yana dizilmiş, kısa aralıklarla tepemizdeki devasa saati kontrol ediyorduk.
Ama ne kadar dik bakarsak bakalım zaman bir türlü istediğimiz hızla ilerlemiyordu. Herkes birkaç dakika sürmesi gereken alelade bir doğa olayına sıkışıp kalmış, karanlıktan sürünerek çıkmayı deniyordu.
Bekleme salonuna doğru döndüm. Nefesimden çıkan buharın arkasında, kalın taş duvarları ve camlarıyla morg kadar güvenli ve soğuk duruyordu. Cesetleri o yüzden bunun gibi yerlere taşımaya başlamışlardı. Demek insanların bütün iyiliği başkaları onları gördüğü içindi ki gündüzleri gecelerden daha karanlık olduğunda hemen birbirlerinin gırtlağına çökmüş, böğürlerinde delikler açmış, gözlerini oyup kafataslarını parçalamışlardı.
İstasyonun ışığı titrediğinde karanlığın enseme saplandığını hissettim. Eğer şimdi, böyle kalabalık bir yerde elektrik kesilse başımıza ne gelirdi?
İçerideki askerlerden biri bakışlarımı yakalayınca yeniden saate odaklanmış gibi yaptım. Sadece birkaç dakika geçmişti.
“Tarlalarım gitti. Böyle boyum kadar ayçiçeği doluydu. Ah, hepsi ölüp gidiyor. Afitap’ın çiçekleri de gi-”
“Dayı, Allah’ını seversen sus. Hepimizi yakacaksın şimdi.”
Karanlıkta durduğunda, görünmez olmayı istemeye başlıyordun. Kimse seni görmemeli, nefesini bile duymamalıydı. Kimsenin de ayağının altında dolaşmamalıydın; gelip kazayla sana çarpmamalılar, takılıp sendelememeliydiler. Yoksa aslında hedefi sen olmadığın bir öfke gürlemeye başlar, yaşadığın ilk şoku ve acıyı silerek üstünden geçerdi.
İlk konuşan, yaşlıca bir adam, kafasında kasketi, nasırlı ellerine hohluyordu. Gözleri ve burnu kızarmıştı. Güneşin kaybolması onun için kendi başına bir felaket değildi. Hayatına olan pratik yansımalarından korkuyordu olsa olsa. Bir anının kaybolması, bu yüzden çoktan kaybettiği birinin biraz daha eksilmesi. Hayatta kalmasını gerektiren sebepler azalırken, hayatta kalmasını sağlayacak kaynaklarını da kaybediyordu.
Onu susturan delikanlıysa atkısını bütün kafasına sarmış, sakalı ve yüzünün derinliklerine kaçmış gözleri dışında bedeninin bütün parçalarını gizlemeye çalışıyordu. İşte o, güneşin kaybolmasının tam olarak ne anlama geldiğini anlamamış olsa bile, dehşetini olduğu gibi hissedebilenlerdendi.
Güneşin onlardan alındıktan sonra kime verileceğini sormuyorlardı. En başta onlara verildiğinde de hiçbir soru sormamışlardı zaten.
İki saat ne zaman geçer?
Midemin üstünde, sağ tarafıma doğru keskin bir acı hissettim. Karaciğerim. Gözlerimi yumdum. Yanımda biri metal bir nesneyi yere bıraktı. Bir kafesti. İçerisindeki kartalın ıslak kokusu burnuma ulaşmadan önce bile biliyordum bunu.
“Yeniden mi?” diye sordu bana kartal. Kanatları kanlı. Zamanın her bir parçası tüylerinin üstüne çöreklenmişti. Gagası bir şey, tahminen et parçası geveliyor gibi hareket ediyordu. Eski anılar kolay unutulmazmış. Şu anda kafesinin kalın parmaklıklarının ardında olsa da bunun bir aldatmaca olduğunu bir tek ben biliyordum. Her an kanatlarını iki yana uzatıverebilir, hava bu hareketiyle dalgalanarak kafesi esneterek hepimizi içine alacak kadar genişleyebilir, parmaklıklar önce ayaklarımızın altına serilir gibi gözükebilir ama aslında hepimizin üstünde yükselerek tepemize çökebilirdi.
Aşağıya baktım. Tahtalarla zapt edilmiş, hiçbir yere gidemeyen ama her yere uzanan tren rayları. Atlayıp koşsam… Çantam çok ağırdı. Daha birkaç adım atamadan, kartal, suratını bedenime gömerdi.
“Bu sefer farklı,” diye yanıtladım onu. “Yeniden diyemezsin. Tekrarladığım bir şey değil bu. Hatta bir hata yapıyormuşum gibi tonlayamazsın da. Bu sefer, insanların hak etmediğini biliyorum.”
“O zaman daha vahim. Süzme salaksın demektir.”
“İnsanların hak etmemesi, insanlığın hak etmediği anlamına gelmez ki.”
Az önce göz göze geldiğim genççe ama çökük asker hâlâ bana bakıyordu. Bir kartalla konuştuğumu anlamamıştı şüphesiz. Yanımdakilerden biriyle konuştuğumu sanmış olmalıydı. Ama konuştuğum kişiye bakmıyordum ona göre. Çekingence kafamı eğmiştim. Bir kez daha göz göze geldiğimizde içerideki diğer iki askere bir şeyler söyledi, onlar dönüp beni süzerken dışarı çıktı.
Yanımızdaki, az önce konuşan iki adam da şaşkınlıkla bir bana bir kartala bakıyordu.
“Yalnız bu sefer kalbin de kırılacak, Prometheus,” dedi kartal, bana. “Belki son olur. Biliyorsun, bir sürü soruna neden oluyor bu yaptıkların.”
Beni koruyordu sözde. En çok kanıma dokunan buydu. Kasıklarımın üstüne oturmuş, kanlı suratının ardında gözleri parlarken attığı çığlık kulaklarımda titremeye devam ediyordu. Bu tabloda kimsenin kimseyi düşündüğü yoktu. Kartalın, yanımızdaki adamların, artık arkama kadar gelmiş olması gereken askerin, tren raylarının, geçmeyen saatlerin…
Arkamı döndüğümde, asker sahiden oradaydı. Zaten öyle olması gerekiyordu; görmüştüm bunu, biliyordum. Kehanetler… Bir şeyler söylüyordu ama ağzı oynarken sesi çıkmıyordu. Yavaşlamış, kendisini saatin akışına uydurmuştu. Havada donan tükürüğünden anlaşılıyordu, sinirliydi. Korktuğu için olduğunu biliyordum. Her seferinde korkmuşlardı. Beni unutmuş olmaları işlerini kolaylaştırmıyordu. Sadece yeni bir isim vermelerine neden oluyordu. Bu seferkiyle beni lanetleyecekleri kesinleşmişti.
Olması gerekenle olanların farklı olması ne kadar acınasıydı. Olması gerekenlerin doğasının kötücül olmasıysa bir yerde buna dayanıyordu.
“Salaksın,” dedi kartal bana. Zamanı aşan bir çığlık. Hepimizin önüne geçmişti ama kimseyi durduramıyordu.
Sonsuzluğa kaç tane iki saat sıkıştırabilirsiniz?
Ben bir tane bile sıkıştıramadım.
Çantama uzanıyordum. Asker de sırtındaki tüfeğini indiriyordu. Benim acelem yoktu, onunsa eli ayağı birbirine dolaşıyordu. Oysaki her şey tam olması gerektiği anda olacaktı. Kehanet başkasının parmaklarının ucundaydı.
Güneş, bir tüfeğin patlamasıyla yeryüzüne doğdu.
Rayların üzerine serilmiş göğsümün ortasından, bir çantanın içinden.
Not: Bu öykü ilk olarak 2021 yılında Esrarengiz Hikâyeler'de yayımlanmıştır.
-
 @ 3f770d65:7a745b24
2024-12-31 17:03:46
@ 3f770d65:7a745b24
2024-12-31 17:03:46Here are my predictions for Nostr in 2025:
Decentralization: The outbox and inbox communication models, sometimes referred to as the Gossip model, will become the standard across the ecosystem. By the end of 2025, all major clients will support these models, providing seamless communication and enhanced decentralization. Clients that do not adopt outbox/inbox by then will be regarded as outdated or legacy systems.
Privacy Standards: Major clients such as Damus and Primal will move away from NIP-04 DMs, adopting more secure protocol possibilities like NIP-17 or NIP-104. These upgrades will ensure enhanced encryption and metadata protection. Additionally, NIP-104 MLS tools will drive the development of new clients and features, providing users with unprecedented control over the privacy of their communications.
Interoperability: Nostr's ecosystem will become even more interconnected. Platforms like the Olas image-sharing service will expand into prominent clients such as Primal, Damus, Coracle, and Snort, alongside existing integrations with Amethyst, Nostur, and Nostrudel. Similarly, audio and video tools like Nostr Nests and Zap.stream will gain seamless integration into major clients, enabling easy participation in live events across the ecosystem.
Adoption and Migration: Inspired by early pioneers like Fountain and Orange Pill App, more platforms will adopt Nostr for authentication, login, and social systems. In 2025, a significant migration from a high-profile application platform with hundreds of thousands of users will transpire, doubling Nostr’s daily activity and establishing it as a cornerstone of decentralized technologies.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28O Planetinha
Fumaça verde me entrando pelas narinas e um coro desafinado fazia uma base melódica.
nos confins da galáxia havia um planetinha isolado. Era um planeta feliz.
O homem vestido de mago começava a aparecer por detrás da fumaça verde.
O planetinha recebeu três presentes, mas o seu habitante, o homem, estava num estado de confusão tão grande que ameaçava estragá-los. Os homens já havia escravizado o primeiro presente, a vida; lutavam contra o segundo presente, a morte; e havia alguns que achavam que deviam destruir totalmente o terceiro, o amor, e com isto levar a desordem total ao pobre planetinha perdido, que se chamava Terra.
O coro desafinado entrou antes do "Terra" cantando várias vezes, como se imitasse um eco, "terra-terra-terraaa". Depois de uma pausa dramática, o homem vestido de mago voltou a falar.
Terra, nossa nave mãe.
Neste momento eu me afastei. À frente do palco onde o mago e seu coral faziam apelos à multidão havia vários estandes cobertos com a tradicional armação de quatro pernas e lona branca. Em todos os cantos da praça havia gente, gente dos mais variados tipos. Visitantes curiosos que se aproximavam atraídos pela fumaça verde e as barraquinhas, gente que aproveitava o movimento para vender doces sem pagar imposto, casais que se abraçavam de pé para espantar o frio, os tradicionais corredores que faziam seu cooper, gente cheia de barba e vestida para imitar os hippies dos anos 60 e vender colares estendidos no chão, transeuntes novos e velhos, vestidos como baladeiros ou como ativistas do ônibus grátis, grupos de ciclistas entusiastas.
O mago fazia agora apelos para que nós, os homens, habitantes do isolado planetinha, passássemos a ver o planetinha, nossa nave mãe, como um todo, e adquiríssemos a consciência de que ele estava entrando em maus lençóis. A idéia, reforçada pela logomarca do evento, era que parássemos de olhar só para a nossa vida e pensássemos no planeta.
A logomarca do evento, um desenho estilizado do planeta Terra, nada tinha a ver com seu nome: "Festival Andando de Bem com a Vida", mas havia sido ali colocada estrategicamente pelos organizadores, de quem parecia justamente sair a mensagem dita pelo mago.
Aquela multidão de pessoas que, assim como eu, tinham suas próprias preocupações, não podiam ver o quadro caótico que formavam, cada uma com seus atos isolados, ali naquela praça isolada, naquele planeta isolado. Quando o hippie barbudo, quase um Osho, assustava um casal para tentar vender-lhes um colar, a quantidade de caos que isto acrescentava à cena era gigantesca. Por um segundo, pude ver, como se estivesse de longe e acima, com toda a pretensão que este estado imaginativo carrega, a cena completa do caos.
Uma nave-mãe, dessas de ficção científica, habitada por milhões de pessoas, seguia no espaço sem rumo, e sem saber que logo à frente um longo precipício espacial a esperava, para a desgraça completa sua e de seus habitantes.
Acostumados àquela nave tanto quanto outrora estiveram acostumados à sua terra natal, os homens viviam as próprias vidas sem nem se lembrar que estavam vagando pelo espaço. Ninguém sabia quem estava conduzindo a nave, e ninguém se importava.
No final do filme descobre-se que era a soma completa do caos que cada habitante produzia, com seus gestos egoístas e incapazes de levar em conta a totalidade, é que determinava a direção da nave-mãe. O efeito, no entanto, não era imediato, como nunca é. Havia gente de verdade encarregada de conduzir a nave, mas era uma gente bêbada, mau-caráter, que vivia brigando pelo controle da nave e o poder que isto lhes dava. Poder, status, dinheiro!
Essa gente bêbada era atraída até ali pela corrupção das instituições e da moral comum que, no fundo no fundo, era causada pelo egoísmo da população, através de um complexo -- mas que no filme aparece simplificado pela ação individual de um magnata do divertimento público -- processo social.
O homem vestido de mago era mais um agente causador de caos, com sua cena cheia de fumaça e sua roupa estroboscópica, ele achava que estava fazendo o bem ao alertar sua platéia, todos as sextas-feiras, de que havia algo que precisava ser feito, que cada um que estava ali ouvindo era responsável pelo planeta. A sua incapacidade, porém, de explicar o que precisava ser feito só aumentava a angústia geral; a culpa que ele jogava sobre seu público, e que era prontamente aceita e passada em frente, aos familiares e amigos de cada um, atormentava-os diariamente e os impedia de ter uma vida decente no trabalho e em casa. As famílias, estressadas, estavam constantemente brigando e os motivos mais insignificantes eram responsáveis pelas mais horrendas conseqüências.
O mago, que após o show tirava o chapéu entortado e ia tomar cerveja num boteco, era responsável por uma parcela considerável do caos que levava a nave na direção do seu desgraçado fim. No filme, porém, um dos transeuntes que de passagem ouviu um pedaço do discurso do mago despertou em si mesmo uma consiência transformadora e, com poderes sobre-humanos que lhe foram então concedidos por uma ordem iniciática do bem ou não, usando só os seus poderes humanos mesmo, o transeunte -- na primeira versão do filme um homem, na segunda uma mulher -- consegue consertar as instituições e retirar os bêbados da condução da máquina. A questão da moral pública é ignorada para abreviar a trama, já com duas horas e quarenta de duração, mas subentende-se que ela também fora resolvida.
No planeta Terra real, que não está indo em direção alguma, preso pela gravidade ao Sol, e onde as pessoas vivem a própria vida porque lhes é impossível viver a dos outros, não têm uma consciência global de nada porque só é possível mesmo ter a consciência delas mesmas, e onde a maioria, de uma maneira ou de outra, está tentando como pode, fazer as coisas direito, o filme é exibido.
Para a maioria dos espectadores, é um filme que evoca reflexões, um filme forte. Por um segundo elas têm o mesmo vislumbre do caos generalizado que eu tive ali naquela praça. Para uma pequena parcela dos espectadores -- entre eles alguns dos que estavam na platéia do mago, o próprio mago, o seguidor do Osho, o casal de duas mulheres e o vendedor de brigadeiros, mas aos quais se somam também críticos de televisão e jornal e gente que fala pelos cotovelos na internet -- o filme é um horror, o filme é uma vulgarização de um problema real e sério, o filme apela para a figura do herói salvador e passa uma mensagem totalmente errada, de que a maioria da população pode continuar vivendo as suas própria vidinhas miseráveis enquanto espera por um herói que vem do Olimpo e os salva da mixórdia que eles mesmos causaram, é um filme que presta um enorme desserviço à causa.
No dia seguinte ao lançamento, num bar meio caro ali perto da praça, numa mesa com oito pessoas, entre elas seis do primeiro grupo e oito do segundo, discute-se se o filme levará ou não o Oscar. Eu estou em casa dormindo e não escuto nada.

