-
 @ a008def1:57a3564d
2025-04-30 17:52:11
@ a008def1:57a3564d
2025-04-30 17:52:11A Vision for #GitViaNostr
Git has long been the standard for version control in software development, but over time, we has lost its distributed nature. Originally, Git used open, permissionless email for collaboration, which worked well at scale. However, the rise of GitHub and its centralized pull request (PR) model has shifted the landscape.
Now, we have the opportunity to revive Git's permissionless and distributed nature through Nostr!
We’ve developed tools to facilitate Git collaboration via Nostr, but there are still significant friction that prevents widespread adoption. This article outlines a vision for how we can reduce those barriers and encourage more repositories to embrace this approach.
First, we’ll review our progress so far. Then, we’ll propose a guiding philosophy for our next steps. Finally, we’ll discuss a vision to tackle specific challenges, mainly relating to the role of the Git server and CI/CD.
I am the lead maintainer of ngit and gitworkshop.dev, and I’ve been fortunate to work full-time on this initiative for the past two years, thanks to an OpenSats grant.
How Far We’ve Come
The aim of #GitViaNostr is to liberate discussions around code collaboration from permissioned walled gardens. At the core of this collaboration is the process of proposing and applying changes. That's what we focused on first.
Since Nostr shares characteristics with email, and with NIP34, we’ve adopted similar primitives to those used in the patches-over-email workflow. This is because of their simplicity and that they don’t require contributors to host anything, which adds reliability and makes participation more accessible.
However, the fork-branch-PR-merge workflow is the only model many developers have known, and changing established workflows can be challenging. To address this, we developed a new workflow that balances familiarity, user experience, and alignment with the Nostr protocol: the branch-PR-merge model.
This model is implemented in ngit, which includes a Git plugin that allows users to engage without needing to learn new commands. Additionally, gitworkshop.dev offers a GitHub-like interface for interacting with PRs and issues. We encourage you to try them out using the quick start guide and share your feedback. You can also explore PRs and issues with gitplaza.
For those who prefer the patches-over-email workflow, you can still use that approach with Nostr through gitstr or the
ngit sendandngit listcommands, and explore patches with patch34.The tools are now available to support the core collaboration challenge, but we are still at the beginning of the adoption curve.
Before we dive into the challenges—such as why the Git server setup can be jarring and the possibilities surrounding CI/CD—let’s take a moment to reflect on how we should approach the challenges ahead of us.
Philosophy
Here are some foundational principles I shared a few years ago:
- Let Git be Git
- Let Nostr be Nostr
- Learn from the successes of others
I’d like to add one more:
- Embrace anarchy and resist monolithic development.
Micro Clients FTW
Nostr celebrates simplicity, and we should strive to maintain that. Monolithic developments often lead to unnecessary complexity. Projects like gitworkshop.dev, which aim to cover various aspects of the code collaboration experience, should not stifle innovation.
Just yesterday, the launch of following.space demonstrated how vibe-coded micro clients can make a significant impact. They can be valuable on their own, shape the ecosystem, and help push large and widely used clients to implement features and ideas.
The primitives in NIP34 are straightforward, and if there are any barriers preventing the vibe-coding of a #GitViaNostr app in an afternoon, we should work to eliminate them.
Micro clients should lead the way and explore new workflows, experiences, and models of thinking.
Take kanbanstr.com. It provides excellent project management and organization features that work seamlessly with NIP34 primitives.
From kanban to code snippets, from CI/CD runners to SatShoot—may a thousand flowers bloom, and a thousand more after them.
Friction and Challenges
The Git Server
In #GitViaNostr, maintainers' branches (e.g.,
master) are hosted on a Git server. Here’s why this approach is beneficial:- Follows the original Git vision and the "let Git be Git" philosophy.
- Super efficient, battle-tested, and compatible with all the ways people use Git (e.g., LFS, shallow cloning).
- Maintains compatibility with related systems without the need for plugins (e.g., for build and deployment).
- Only repository maintainers need write access.
In the original Git model, all users would need to add the Git server as a 'git remote.' However, with ngit, the Git server is hidden behind a Nostr remote, which enables:
- Hiding complexity from contributors and users, so that only maintainers need to know about the Git server component to start using #GitViaNostr.
- Maintainers can easily swap Git servers by updating their announcement event, allowing contributors/users using ngit to automatically switch to the new one.
Challenges with the Git Server
While the Git server model has its advantages, it also presents several challenges:
- Initial Setup: When creating a new repository, maintainers must select a Git server, which can be a jarring experience. Most options come with bloated social collaboration features tied to a centralized PR model, often difficult or impossible to disable.
-
Manual Configuration: New repositories require manual configuration, including adding new maintainers through a browser UI, which can be cumbersome and time-consuming.
-
User Onboarding: Many Git servers require email sign-up or KYC (Know Your Customer) processes, which can be a significant turn-off for new users exploring a decentralized and permissionless alternative to GitHub.
Once the initial setup is complete, the system works well if a reliable Git server is chosen. However, this is a significant "if," as we have become accustomed to the excellent uptime and reliability of GitHub. Even professionally run alternatives like Codeberg can experience downtime, which is frustrating when CI/CD and deployment processes are affected. This problem is exacerbated when self-hosting.
Currently, most repositories on Nostr rely on GitHub as the Git server. While maintainers can change servers without disrupting their contributors, this reliance on a centralized service is not the decentralized dream we aspire to achieve.
Vision for the Git Server
The goal is to transform the Git server from a single point of truth and failure into a component similar to a Nostr relay.
Functionality Already in ngit to Support This
-
State on Nostr: Store the state of branches and tags in a Nostr event, removing reliance on a single server. This validates that the data received has been signed by the maintainer, significantly reducing the trust requirement.
-
Proxy to Multiple Git Servers: Proxy requests to all servers listed in the announcement event, adding redundancy and eliminating the need for any one server to match GitHub's reliability.
Implementation Requirements
To achieve this vision, the Nostr Git server implementation should:
-
Implement the Git Smart HTTP Protocol without authentication (no SSH) and only accept pushes if the reference tip matches the latest state event.
-
Avoid Bloat: There should be no user authentication, no database, no web UI, and no unnecessary features.
-
Automatic Repository Management: Accept or reject new repositories automatically upon the first push based on the content of the repository announcement event referenced in the URL path and its author.
Just as there are many free, paid, and self-hosted relays, there will be a variety of free, zero-step signup options, as well as self-hosted and paid solutions.
Some servers may use a Web of Trust (WoT) to filter out spam, while others might impose bandwidth or repository size limits for free tiers or whitelist specific npubs.
Additionally, some implementations could bundle relay and blossom server functionalities to unify the provision of repository data into a single service. These would likely only accept content related to the stored repositories rather than general social nostr content.
The potential role of CI / CD via nostr DVMs could create the incentives for a market of highly reliable free at the point of use git servers.
This could make onboarding #GitViaNostr repositories as easy as entering a name and selecting from a multi-select list of Git server providers that announce via NIP89.
!(image)[https://image.nostr.build/badedc822995eb18b6d3c4bff0743b12b2e5ac018845ba498ce4aab0727caf6c.jpg]
Git Client in the Browser
Currently, many tasks are performed on a Git server web UI, such as:
- Browsing code, commits, branches, tags, etc.
- Creating and displaying permalinks to specific lines in commits.
- Merging PRs.
- Making small commits and PRs on-the-fly.
Just as nobody goes to the web UI of a relay (e.g., nos.lol) to interact with notes, nobody should need to go to a Git server to interact with repositories. We use the Nostr protocol to interact with Nostr relays, and we should use the Git protocol to interact with Git servers. This situation has evolved due to the centralization of Git servers. Instead of being restricted to the view and experience designed by the server operator, users should be able to choose the user experience that works best for them from a range of clients. To facilitate this, we need a library that lowers the barrier to entry for creating these experiences. This library should not require a full clone of every repository and should not depend on proprietary APIs. As a starting point, I propose wrapping the WASM-compiled gitlib2 library for the web and creating useful functions, such as showing a file, which utilizes clever flags to minimize bandwidth usage (e.g., shallow clone, noblob, etc.).
This approach would not only enhance clients like gitworkshop.dev but also bring forth a vision where Git servers simply run the Git protocol, making vibe coding Git experiences even better.
song
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 created song with a complementary vision that has shaped how I see the role of the git server. Its a self-hosted, nostr-permissioned git server with a relay baked in. Its currently a WIP and there are some compatability with ngit that we need to work out.
We collaborated on the nostr-permissioning approach now reflected in nip34.
I'm really excited to see how this space evolves.
CI/CD
Most projects require CI/CD, and while this is often bundled with Git hosting solutions, it is currently not smoothly integrated into #GitViaNostr yet. There are many loosely coupled options, such as Jenkins, Travis, CircleCI, etc., that could be integrated with Nostr.
However, the more exciting prospect is to use DVMs (Data Vending Machines).
DVMs for CI/CD
Nostr Data Vending Machines (DVMs) can provide a marketplace of CI/CD task runners with Cashu for micro payments.
There are various trust levels in CI/CD tasks:
- Tasks with no secrets eg. tests.
- Tasks using updatable secrets eg. API keys.
- Unverifiable builds and steps that sign with Android, Nostr, or PGP keys.
DVMs allow tasks to be kicked off with specific providers using a Cashu token as payment.
It might be suitable for some high-compute and easily verifiable tasks to be run by the cheapest available providers. Medium trust tasks could be run by providers with a good reputation, while high trust tasks could be run on self-hosted runners.
Job requests, status, and results all get published to Nostr for display in Git-focused Nostr clients.
Jobs could be triggered manually, or self-hosted runners could be configured to watch a Nostr repository and kick off jobs using their own runners without payment.
But I'm most excited about the prospect of Watcher Agents.
CI/CD Watcher Agents
AI agents empowered with a NIP60 Cashu wallet can run tasks based on activity, such as a push to master or a new PR, using the most suitable available DVM runner that meets the user's criteria. To keep them running, anyone could top up their NIP60 Cashu wallet; otherwise, the watcher turns off when the funds run out. It could be users, maintainers, or anyone interested in helping the project who could top up the Watcher Agent's balance.
As aluded to earlier, part of building a reputation as a CI/CD provider could involve running reliable hosting (Git server, relay, and blossom server) for all FOSS Nostr Git repositories.
This provides a sustainable revenue model for hosting providers and creates incentives for many free-at-the-point-of-use hosting providers. This, in turn, would allow one-click Nostr repository creation workflows, instantly hosted by many different providers.
Progress to Date
nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr and nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 have been working on a runner that uses GitHub Actions YAML syntax (using act) for the dvm-cicd-runner and takes Cashu payment. You can see example runs on GitWorkshop. It currently takes testnuts, doesn't give any change, and the schema will likely change.
Note: The actions tab on GitWorkshop is currently available on all repositories if you turn on experimental mode (under settings in the user menu).
It's a work in progress, and we expect the format and schema to evolve.
Easy Web App Deployment
For those disapointed not to find a 'Nostr' button to import a git repository to Vercel menu: take heart, they made it easy. vercel.com_import_options.png there is a vercel cli that can be easily called in CI / CD jobs to kick of deployments. Not all managed solutions for web app deployment (eg. netlify) make it that easy.
Many More Opportunities
Large Patches via Blossom
I would be remiss not to mention the large patch problem. Some patches are too big to fit into Nostr events. Blossom is perfect for this, as it allows these larger patches to be included in a blossom file and referenced in a new patch kind.
Enhancing the #GitViaNostr Experience
Beyond the large patch issue, there are numerous opportunities to enhance the #GitViaNostr ecosystem. We can focus on improving browsing, discovery, social and notifications. Receiving notifications on daily driver Nostr apps is one of the killer features of Nostr. However, we must ensure that Git-related notifications are easily reviewable, so we don’t miss any critical updates.
We need to develop tools that cater to our curiosity—tools that enable us to discover and follow projects, engage in discussions that pique our interest, and stay informed about developments relevant to our work.
Additionally, we should not overlook the importance of robust search capabilities and tools that facilitate migrations.
Concluding Thoughts
The design space is vast. Its an exciting time to be working on freedom tech. I encourage everyone to contribute their ideas and creativity and get vibe-coding!
I welcome your honest feedback on this vision and any suggestions you might have. Your insights are invaluable as we collaborate to shape the future of #GitViaNostr. Onward.
Contributions
To conclude, I want to acknowledge some the individuals who have made recent code contributions related to #GitViaNostr:
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 (gitstr, song, patch34), nostr:npub1useke4f9maul5nf67dj0m9sq6jcsmnjzzk4ycvldwl4qss35fvgqjdk5ks (gitplaza)
nostr:npub1elta7cneng3w8p9y4dw633qzdjr4kyvaparuyuttyrx6e8xp7xnq32cume (ngit contributions, git-remote-blossom),nostr:npub16p8v7varqwjes5hak6q7mz6pygqm4pwc6gve4mrned3xs8tz42gq7kfhdw (SatShoot, Flotilla-Budabit), nostr:npub1ehhfg09mr8z34wz85ek46a6rww4f7c7jsujxhdvmpqnl5hnrwsqq2szjqv (Flotilla-Budabit, Nostr Git Extension), nostr:npub1ahaz04ya9tehace3uy39hdhdryfvdkve9qdndkqp3tvehs6h8s5slq45hy (gnostr and experiments), and others.
nostr:npub1uplxcy63up7gx7cladkrvfqh834n7ylyp46l3e8t660l7peec8rsd2sfek (git-remote-nostr)
Project Management nostr:npub1ltx67888tz7lqnxlrg06x234vjnq349tcfyp52r0lstclp548mcqnuz40t (kanbanstr) Code Snippets nostr:npub1ygzj9skr9val9yqxkf67yf9jshtyhvvl0x76jp5er09nsc0p3j6qr260k2 (nodebin.io) nostr:npub1r0rs5q2gk0e3dk3nlc7gnu378ec6cnlenqp8a3cjhyzu6f8k5sgs4sq9ac (snipsnip.dev)
CI / CD nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr
and for their nostr:npub1c03rad0r6q833vh57kyd3ndu2jry30nkr0wepqfpsm05vq7he25slryrnw nostr:npub1qqqqqq2stely3ynsgm5mh2nj3v0nk5gjyl3zqrzh34hxhvx806usxmln03 and nostr:npub1l5sga6xg72phsz5422ykujprejwud075ggrr3z2hwyrfgr7eylqstegx9z for their testing, feedback, ideas and encouragement.
Thank you for your support and collaboration! Let me know if I've missed you.
-
 @ c230edd3:8ad4a712
2025-04-30 16:19:30
@ c230edd3:8ad4a712
2025-04-30 16:19:30Chef's notes
I found this recipe on beyondsweetandsavory.com. The site is incredibly ad infested (like most recipe sites) and its very annoying so I'm copying it to Nostr so all the homemade ice cream people can access it without dealing with that mess. I haven't made it yet. Will report back, when I do.
Details
- ⏲️ Prep time: 20 min
- 🍳 Cook time: 55 min
- 🍽️ Servings: 8
Ingredients
- 2 cups heavy cream
- 1 cup 2% milk
- 8 oz dark chocolate, 70%
- ¼ cup Dutch cocoa
- 2 tbsps loose Earl grey tea leaves
- 4 medium egg yolks
- ¾ cup granulated sugar
- ⅛ tsp salt
- ¼ cup dark chocolate, 70% chopped
Directions
- In a double boiler or a bowl set over a saucepan of simmering water, add the cacao solids and ½ cup of heavy cream. Stir chocolate until melted and smooth. Set melted chocolate aside.
- In a heavy saucepan, combine remaining heavy cream, milk, salt and ½ cup of sugar.
- Put the pan over medium heat and let the mixture boil gently to bubbling just around the edges (gentle simmer) and sugar completely dissolved, about 5 minutes. Remove from heat.
- Add the Earl Grey tea leaves and let it steep for 7-8 minutes until the cream has taken on the tea flavor, stirring occasionally and tasting to make sure it’s not too bitter.
- Whisk in Dutch cocoa until smooth. Add in melted chocolate and whisk until smooth.
- In a medium heatproof bowl, whisk the yolks just to break them up and whisk in remaining sugar. Set aside.
- Put the saucepan back on the stove over low heat and let it warm up for 2 minutes.
- Carefully measure out ½ cup of hot cream mixture.
- While whisking the eggs constantly, whisk the hot cream mixture into the eggs until smooth. Continue tempering the eggs by adding another ½ cup of hot cream to the bowl with the yolks.
- Pour the cream-egg mixture back to the saucepan and cook over medium-low heat, stirring constantly until it is thickened and coats the back of a spatula, about 5 minutes.
- Strain the base through a fine-mesh strainer into a clean container.
- Pour the mixture into a 1-gallon Ziplock freezer bag and submerge the sealed bag in an ice bath until cold, about 30 minutes. Refrigerate the ice cream base for at least 4 hours or overnight.
- Pour the ice cream base into the frozen canister of your ice cream machine and follow the manufacturer’s instructions.
- Spin until thick and creamy about 25-30 minutes.
- Pack the ice cream into a storage container, press a sheet of parchment directly against the surface and seal with an airtight lid. Freeze in the coldest part of your freezer until firm, at least 4 hours.
- When ready to serve, scoop the ice cream into a serving bowl and top with chopped chocolate.
-
 @ 1739d937:3e3136ef
2025-04-30 14:39:24
@ 1739d937:3e3136ef
2025-04-30 14:39:24MLS over Nostr - 30th April 2025
YO! Exciting stuff in this update so no intro, let's get straight into it.
🚢 Libraries Released
I've created 4 new Rust crates to make implementing NIP-EE (MLS) messaging easy for other projects. These are now part of the rust-nostr project (thanks nostr:npub1drvpzev3syqt0kjrls50050uzf25gehpz9vgdw08hvex7e0vgfeq0eseet) but aren't quite released to crates.io yet. They will be included in the next release of that library. My hope is that these libraries will give nostr developers a simple, safe, and specification-compliant way to work with MLS messaging in their applications.
Here's a quick overview of each:
nostr_mls_storage
One of the challenges of using MLS messaging is that clients have to store quite a lot of state about groups, keys, and messages. Initially, I implemented all of this in White Noise but knew that eventually this would need to be done in a more generalized way.
This crate defines traits and types that are used by the storage implementation crates and sets those up to wrap the OpenMLS storage layer. Now, instead of apps having to implement storage for both OpenMLS and Nostr, you simply pick your storage backend and go from there.
Importantly, because these are generic traits, it allows for the creation of any number of storage implementations for different backend storage providers; postgres, lmdb, nostrdb, etc. To start I've created two implementations; detailed below.
nostr_mls_memory_storage
This is a simple implementation of the nostr_mls_storage traits that uses an in-memory store (that doesn't persist anything to disc). This is principally for testing.
nostr_mls_sqlite_storage
This is a production ready implementation of the nostr_mls_storage traits that uses a persistent local sqlite database to store all data.
nostr_mls
This is the main library that app developers will interact with. Once you've chose a backend and instantiated an instance of NostrMls you can then interact with a simple set of methods to create key packages, create groups, send messages, process welcomes and messages, and more.
If you want to see a complete example of what the interface looks like check out mls_memory.rs.
I'll continue to add to this library over time as I implement more of the MLS protocol features.
🚧 White Noise Refactor
As a result of these new libraries, I was able to remove a huge amount of code from White Noise and refactor large parts of the app to make the codebase easier to understand and maintain. Because of this large refactor and the changes in the underlying storage layer, if you've installed White Noise before you'll need to delete it from your device before you trying to install again.
🖼️ Encrypted Media with Blossom
Let's be honest: Group chat would be basically useless if you couldn't share memes and gifs. Well, now you can in White Noise. Media in groups is encrypted using an MLS secret and uploaded to Blossom with a one-time use keypair. This gives groups a way to have rich conversations with images and documents and anything else while also maintaining the privacy and security of the conversation.
This is still in a rough state but rendering improvements are coming next.
📱 Damn Mobile
The app is still in a semi-broken state on Android and fully broken state on iOS. Now that I have the libraries released and the White Noise core code refactored, I'm focused 100% on fixing these issues. My goal is to have a beta version live on Zapstore in a few weeks.
🧑💻 Join Us
I'm looking for mobile developers on both Android and iOS to join the team and help us build the best possible apps for these platforms. I have grant funding available for the right people. Come and help us build secure, permissionless, censorship-resistant messaging. I can think of few projects that deserve your attention more than securing freedom of speech and freedom of association for the entire world. If you're interested or know someone who might be, please reach out to me directly.
🙏 Thanks to the People
Last but not least: A HUGE thank you to all the folks that have been helping make this project happen. You can check out the people that are directly working on the apps on Following._ (and follow them). There are also a lot of people behind the scenes that have helped in myriad ways to get us this far. Thank you thank you thank you.
🔗 Links
Libraries
White Noise
Other
-
 @ 4e616576:43c4fee8
2025-04-30 13:28:18
@ 4e616576:43c4fee8
2025-04-30 13:28:18asdfasdfsadfaf
-
 @ 4e616576:43c4fee8
2025-04-30 13:27:51
@ 4e616576:43c4fee8
2025-04-30 13:27:51asdfasdf
-
 @ 4e616576:43c4fee8
2025-04-30 13:13:51
@ 4e616576:43c4fee8
2025-04-30 13:13:51asdffasdf
-
 @ 4e616576:43c4fee8
2025-04-30 13:11:58
@ 4e616576:43c4fee8
2025-04-30 13:11:58asdfasdfasfd
-
 @ 81650982:299380fa
2025-04-30 11:16:42
@ 81650982:299380fa
2025-04-30 11:16:42Let us delve into Monero (XMR). Among the proponents of various altcoins, Monero arguably commands one of the most dedicated followings, perhaps second only to Ethereum. Unlike many altcoins where even investors often harbor speculative, short-term intentions, the genuine belief within the Monero community suggests an inherent appeal to the chain itself.
The primary advantage touted by Monero (and similar so-called "privacy coins") is its robust privacy protection features. The demand for anonymous payment systems, tracing its lineage back to David Chaum, predates even the inception of Bitcoin. Monero's most heavily promoted strength, relative to Bitcoin, is that its privacy features are enabled by default.
This relates to the concept of the "anonymity set." To guarantee anonymity, a user must blend into a crowd of ordinary users. The larger the group one hides within, the more difficult it becomes for an external observer to identify any specific individual. From the perspective of Monero advocates, Bitcoin's default transaction model is overly transparent, clearly revealing the flow of funds between addresses. While repeated mixing can enhance anonymity in Bitcoin, the fact that users must actively undertake such measures presents a significant hurdle. More critically, proponents argue, the very group engaging in such deliberate obfuscation is precisely the group one doesn't want to be associated with for effective anonymity. Hiding requires blending with the ordinary, not merely mixing with others who are also actively trying to hide — the latter, they contend, is akin to criminals mixing only with other criminals.
This is a valid point. For instance, there's a substantial difference between a messenger app offering end-to-end encryption for all communications by default, versus one requiring users to explicitly create a "secret chat" for encryption. While I personally believe that increased self-custody of Bitcoin in personal wallets, acquisition through direct peer-to-peer payments rather than exchange purchases, and the widespread adoption of the Lightning Network would make tracing significantly harder even without explicit mixing efforts, let us concede, for the sake of argument, that Bitcoin's base-layer anonymity might not drastically improve even in such a future scenario.
Nevertheless, Monero's long-term prospects appear considerably constrained when focusing purely on technical limitations, setting aside economic factors or incentive models for now. While discussions on economics can often be countered with "That's just your speculation," technical constraints present more objective facts and leave less room for dispute.
Monero's most fundamental problem is its lack of scalability. To briefly explain how Monero obfuscates the sender: it includes other addresses alongside the true sender's address in the 'from' field and attaches what appears to be valid signatures for all of them. With a default setting of 10 decoys (plus the real spender, making a ring size of 11), the signature size naturally becomes substantially larger than Bitcoin's. Since an observer cannot determine which of the 11 is the true sender, and these decoys are arbitrary outputs selected from the blockchain belonging to other users, anonymity is indeed enhanced. While the sender cannot generate individually valid signatures for the decoy outputs (as they don't own the private keys), the use of a ring signature mathematically proves that one member of the ring authorized the transaction, allowing it to pass network validation.
The critical issue is that this results in transaction sizes several times larger than Bitcoin's. Bitcoin already faces criticism for being relatively expensive and slow. Monero's structure imposes a burden that is multiples greater. One might question the relationship between transaction data size and transaction fees/speed. However, the perceived slowness of blockchains isn't typically due to inefficient code, but rather the strict limitations imposed on block size (or equivalent throughput constraints) to maintain decentralization. Therefore, larger transaction sizes directly translate into throughput limitations and upward pressure on fees. If someone claims Monero fees are currently lower than Bitcoin's, that is merely a consequence of its significantly lower usage. Should Monero's transaction volume reach even a fraction of Bitcoin's, its current architecture would struggle severely under the load.
To address this, Monero implemented a dynamic block size limit instead of a hardcoded one. However, this is not a comprehensive solution. If the block size increases proportionally with usage, a future where Monero achieves widespread adoption as currency — implying usage potentially hundreds, thousands, or even hundreds of thousands of times greater than today — would render the blockchain size extremely difficult to manage for ordinary node operators. Global internet traffic might be consumed by Monero transactions, or at the very least, the bandwidth and storage costs could exceed what individuals can reasonably bear.
Blockchains, by their nature, must maintain a size manageable enough for individuals to run full nodes, necessitating strict block size limits (or equivalent constraints in blockless designs). This fundamental requirement is the root cause of limited transaction speed and rising fees. Consequently, the standard approach to blockchain scaling involves Layer 2 solutions like the Lightning Network. The problem is, implementing such solutions on Monero is extremely challenging.
Layer 2 solutions, while varying in specific implementation details across different blockchains, generally rely heavily on the transparency of on-chain transactions. They typically involve sophisticated smart contracts built upon the ability to publicly verify on-chain states and events. Monero's inherent opacity, hiding crucial details of on-chain transactions, makes it exceptionally difficult for two mutually untrusting parties to reach the necessary consensus and cryptographic agreements (like establishing payment channels with verifiable state transitions and dispute mechanisms) that underpin such Layer 2 systems. The fact that Monero, despite existing for several years, still lacks a functional, widely adopted Layer 2 implementation suggests that this remains an unsolved and technically formidable challenge. While theoretical proposals exist, their real-world feasibility remains uncertain and would likely require significant breakthroughs in cryptographic protocol design.
Furthermore, Monero faces another severe scaling challenge related to its core privacy mechanism. As mentioned, decoy outputs are used to obscure the true sender. An astute observer might wonder: If a third party cannot distinguish the real spender, could the real spender potentially double-spend their funds later? Or could someone's funds become unusable simply because they were chosen as a decoy in another transaction? Naturally, Monero's developers anticipated this. The solution employed involves key images.
When an output is genuinely spent within a ring signature, a unique cryptographic identifier called a "key image" is derived from the real output and the spender's private key. This derivation is one-way (the key image cannot be used to reveal the original output or key). This key image is recorded on the blockchain. When validating a new transaction, the network checks if the submitted key image has already appeared in the history. If it exists, the transaction is rejected as a double-spend attempt. The crucial implication is that this set of used key images can never be pruned. Deleting historical key images would directly enable double-spending.
Therefore, Monero's state size — the data that full nodes must retain and check against — grows linearly and perpetually with the total number of transactions ever processed on the network.
Summary In summary, Monero faces critical technical hurdles:
Significantly Larger Transaction Sizes: The use of ring signatures for anonymity results in transaction data sizes several times larger than typical cryptocurrencies like Bitcoin.
Inherent Scalability Limitations: The large transaction size, combined with the necessity of strict block throughput limits to preserve decentralization, creates severe scalability bottlenecks regarding transaction speed and cost under significant load. Dynamic block sizes, while helpful in the short term, do not constitute a viable long-term solution for broad decentralization.
Layer 2 Implementation Difficulty: Monero's fundamental opacity makes implementing established Layer 2 scaling solutions (like payment channels) extremely difficult with current approaches. The absence of a widely adopted solution to date indicates that this remains a major unresolved challenge.
Unprunable, Linearly Growing State: The key image mechanism required to prevent double-spending mandates the perpetual storage of data proportional to the entire transaction history, unlike Bitcoin where nodes can prune historical blocks and primarily need to maintain the current UTXO set (whose size depends on usage patterns, not total history).
These technical constraints raise legitimate concerns about Monero's ability to scale effectively and achieve widespread adoption in the long term. While ongoing research may alleviate some of these issues, at present they represent formidable challenges that any privacy-focused cryptocurrency must contend with.
-
 @ e096a89e:59351479
2025-04-30 12:59:28
@ e096a89e:59351479
2025-04-30 12:59:28Why Oshi?
I had another name for this brand before, but it was hard for folks to say. Then I saw a chance to tap into the #Nostr and #Bitcoin crowd, people who might vibe with what I’m creating, and I knew I needed something that’d stick.
A good name can make a difference. Well, sometimes. Take Blink-182 - it might sound odd, but it worked for them and even has a ring to it. So, why Oshi?
Names mean a lot to me, and Oshi’s got layers. I’m into Japanese culture and Bitcoin, so it fits perfectly with a few meanings baked in:
- It’s a nod to Bitcoin’s visionary, Satoshi Nakamoto.
- In Japanese, “oshi” means cheering on your favorite idol by supporting their work - think of me as the maker, you as the fan.
- It’s short for “oh shiiiitttt” - what most folks say when they taste how good this stuff is.
My goal with Oshi is to share how amazing pecans and dates can be together. Everything I make - Hodl Butter, Hodl Bars, chocolates - is crafted with intention, keeping it simple and nuanced, no overdoing it. It’s healthy snacking without the grains or junk you find in other products.
I’ve got a few bars and jars in stock now. Grab something today and taste the unique flavor for yourself. Visit my website at https://oshigood.us/
foodstr #oshigood #hodlbar #hodlbutter
-
 @ 88cc134b:5ae99079
2025-04-30 12:55:37
@ 88cc134b:5ae99079
2025-04-30 12:55:37nostr:nevent1qvzqqqqqqypzpzxvzd935e04fm6g4nqa7dn9qc7nafzlqn4t3t6xgmjkr3dwnyreqyvhwumn8ghj7urjv4kkjatd9ec8y6tdv9kzumn9wshszymhwden5te0wp6hyurvv4cxzeewv4ej7qpqx9an7hcqyevak03eefm8dluhn6frcryph6ua069w7d8c8784zcwqwxgp2r
-
 @ e4950c93:1b99eccd
2025-04-30 09:29:25
@ e4950c93:1b99eccd
2025-04-30 09:29:25 -
 @ 4e616576:43c4fee8
2025-04-30 12:53:36
@ 4e616576:43c4fee8
2025-04-30 12:53:36sdfafd
-
 @ 3589b793:ad53847e
2025-04-30 12:40:42
@ 3589b793:ad53847e
2025-04-30 12:40:42※本記事は別サービスで2022年6月24日に公開した記事の移植です。
どうも、「NostrはLNがWeb統合されマネーのインターネットプロトコルとしてのビットコインが本気出す具体行動のショーケースと見做せばOK」です、こんばんは。
またまた実験的な試みがNostrで行われているのでレポートします。本シリーズはライブ感を重視しており、例によって(?)プルリクエストなどはレビュー段階なのでご承知おきください。
今回の主役はあくまでLightningNetworkの新提案(ただし以前からあるLSATからのリブランディング)となるLightning HTTP 402 Protocol(略称: L402)です。そのショーケースの一つとしてNostrが活用されているというものになります。
Lightning HTTP 402 Protocol(略称: L402)とは何か
bLIPに今月挙がったプロポーザル内容です。
https://github.com/lightning/blips/pull/26
L402について私はまだ完全に理解した段階ではあるのですがなんとか一言で説明しようとすると「Authトークンのように"Paid"トークンをHTTPヘッダーにアタッチして有料リソースへのHTTPリクエストの受け入れ判断を行えるようにする」ものだと解釈しました。
Authenticationでは、HTTPヘッダーにAuthトークンを添付し、その検証が通ればHTTPリクエストを許可し、通らなければ
401 Unauthorizedコードをエラーとして返すように定められています。https://developer.mozilla.org/ja/docs/Web/HTTP/Status/401
L402では、同じように、HTTPヘッダーに支払い済みかどうかを示す"Paid"トークンを添付し、その検証が通ればHTTPリクエストを許可し、通らなければ
402 Payment Requiredコードをエラーとして返すようにしています。なお、"Paid"トークンという用語は私の造語となります。便宜上本記事では使わせていただきますが、実際はAuthも入ってくるのが必至ですし、プルリクエストでも用語をどう定めるかは議論になっていることをご承知おきください。("API key", "credentials", "token", らが登場しています)
この402ステータスコードは従来から定義されていましたが、MDNのドキュメントでも記載されているように「実験的」なものでした。つまり、器は用意されているがこれまで活用されてこなかったものとなり、本プロトコルの物語性を体現しているものとなります。
https://developer.mozilla.org/ja/docs/Web/HTTP/Status/402
幻であったHTTPステータスコード402 Payment Requiredを実装する
この物語性は、上述のbLIPのスペックにも詳述されていますが、以下のスライドが簡潔です。
402 Payment Requiredは予約されていましたが、けっきょくのところWorldWideWebはペイメントプロトコルを実装しなかったので、Bitcoinの登場まで待つことになった、というのが要旨になります。このWorldWideWebにおける決済機能実装に関する歴史話はクリプト界隈でもたびたび話題に上がりますが、そこを繋いでくる文脈にこれこそマネーのインターネットプロトコルだなと痺れました。https://x.com/AlyseKilleen/status/1671342634307297282
この"Paid"トークンによって実現できることとして、第一にAIエージェントがBitcoin/LNを自律的に利用できるようになるM2M(MachineToMachine)的な話が挙げられていますが、ユースケースは想像力がいろいろ要るところです。実際のところは「有料リソースへの認可」を可能にすることが主になると理解しました。本連載では、繰り返しNostrクライアントにLNプロトコルを直接搭載せずにLightningNetworkを利用可能にする組み込み方法を見てきましたが、本件もインボイス文字列 & preimage程度の露出になりアプリケーション側でノードやウォレットの実装が要らないので、その文脈で位置付ける解釈もできるかと思います。
Snortでのサンプル実装
LN組み込み業界のリーディングプロダクトであるSnortのサンプル実装では、L402を有料コンテンツの購読に活用しています。具体的には画像や動画を投稿するときに有料のロックをかける、いわゆるペイウォールの一種となります。もともとアップローダもSnortが自前で用意しているので、そこにL402を組み込んでみたということのようです。
体験方法の詳細はこちらにあります。 https://njump.me/nevent1qqswr2pshcpawk9ny5q5kcgmhak24d92qzdy98jm8xcxlgxstruecccpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszrnhwden5te0dehhxtnvdakz78pvlzg
上記を試してみた結果が以下になります。まず、ペイウォールでロックした画像がNostrに投稿されている状態です。まったくビューワーが実装されておらず、ただのNotFound状態になっていますが、支払い前なのでロックされているということです。

次にこのHTTP通信の内容です。

通信自体はエラーになっているわけですが、ステータスコードが402で、レスポンスヘッダーのWWW-AuthenticateにInvoice文字列が返ってきています。つまり、このインボイスを支払えば"Paid"トークンが付与されて、その"Paid"トークンがあれば最初の画像がアンロックされることとなります。残念ながら現在は日本で利用不可のStrikeAppでしか払込みができないためここまでとなりますが、本懐である
402 Payment Requiredとインボイス文字列は確認できました。今確認できることは以上ですが、AmethystやDamusなどの他のNostrクライアントが実装するにあたり、インラインメディアを巡ってL402の仕様をアップデートする必要性や同じくHTTPヘッダーへのAuthトークンとなるNIP-98と組み合わせるなどの議論が行われている最中です。
LinghtningNetworkであるからこそのL402の実現
"Paid"トークンを実現するためにはLightningNetworkのファイナリティが重要な要素となっています。逆に言うと、reorgによるひっくり返しがあり得るBitcoinではできなくもないけど不便なわけです。LightningNetworkなら、当事者である二者間で支払いが確認されたら「同期的」にその証であるハッシュ値を用いて"Paid"トークンを作成することができます。しかもハッシュ値を提出するだけで台帳などで過去の履歴を確認する必要がありません。加えて言うと、受金者側が複数のノードを建てていて支払いを受け取るノードがどれか一つになる状況でも、つまり、スケーリングされている状況でも、"Paid"トークンそのものはどのノードかを気にすることなくステートレスで利用できるとのことです。(ここは単にreverse proxyとしてAuthサーバががんばっているだけと解釈することもできますがずいぶんこの機能にも力点を置いていて大規模なユースケースが重要になっているのだなという印象を抱きました)
Macaroonの本領発揮か?それとも詳細定義しすぎか?
HTTP通信ではWWW-Authenticateの実値にmacaroonの記述が確認できます。また現在のL402スペックでも"Paid"トークンにはmacaroonの利用が前提になっています。
このmacaroonとは(たぶん)googleで研究開発され、LNDノードソフトウェアで活用されているCookieを超えるという触れ込みのデータストアになります。しかし、あまり普及しなかった技術でもあり、個人の感想ですがなんとも微妙なものになっています。
https://research.google/pubs/macaroons-cookies-with-contextual-caveats-for-decentralized-authorization-in-the-cloud/
macaroonの強みは、Cookieを超えるという触れ込みのようにブラウザが無くてもプロセス間通信でデータ共有できる点に加えて、HMACチェーンで動的に認証認可を更新し続けられるところが挙げられます。しかし、そのようなユースケースがあまり無く、静的な認可となるOAuthやJWTで十分となっているのが現状かと思います。
L402では、macaroonの動的な更新が可能である点を活かして、"Paid"トークンを更新するケースが挙げられています。わかりやすいのは上記のスライド資料でも挙げられている"Dynamic Pricing"でしょうか。プロポーザルではloop©️LightningLabsにおいて月間の最大取引量を認可する"Paid"トークンを発行した上でその条件を動向に応じて動的に変更できる例が解説されています。とはいえ、そんなことしなくても再発行すればええやんけという話もなくもないですし、プルリクエストでも仕様レベルでmacaroonを指定するのは「具体」が過ぎるのではないか、もっと「抽象」し単なる"Opaque Token"程度の粒度にして他の実装も許容するべきではないか、という然るべきツッコミが入っています。
個人的にはそのツッコミが妥当と思いつつも、なんだかんだ初めてmacaroonの良さを実感できて感心した次第です。
-
 @ e4950c93:1b99eccd
2025-04-30 09:28:38
@ e4950c93:1b99eccd
2025-04-30 09:28:38 -
 @ 3589b793:ad53847e
2025-04-30 12:28:25
@ 3589b793:ad53847e
2025-04-30 12:28:25※本記事は別サービスで2023年4月19日に公開した記事の移植です。
どうも、「NostrはLNがWeb統合されマネーのインターネットプロトコルとしてのビットコインが本気出す具体行動のショーケースと見做せばOK」です、こんにちは。
前回まで投げ銭や有料購読の組み込み方法を見てきました。
zapsという投げ銭機能が各種クライアントに一通り実装されて活用が進んでいることで、統合は次の段階へ移り始めています。「作戦名: ウォレットをNostrクライアントに組み込め」です。今回はそちらをまとめます。
投げ銭する毎にいちいちウォレットを開いてまた元のNostrクライアントに手動で戻らないといけない is PAIN
LNとNostrはインボイス文字列で繋がっているだけの疎結合ですが、投稿に投げ銭するためには何かのLNウォレットを開いて支払いをして、また元のNostrクライアントに戻る操作をユーザーが手作業でする必要があります。お試しで一回やる程度では気になりませんが普段使いしているとこれはけっこうな煩わしさを感じるUXです。特にスマホでは大変にだるい状況になります。連打できない!
2月の実装以来、zapsは順調に定着して日々投げられています。


https://stats.nostr.band/#daily_zaps
なので、NostrクライアントにLNウォレットの接続を組み込み、支払いのために他のアプリに遷移せずにNostクライアント単独で完結できるようなアップデートが始まっています。
Webクライアント
NostrのLN組み込み業界のリーディングプレイヤーであるSnortでの例です。以下のようにヘッダーのウォレットアイコンをクリックすると連携ウォレットの選択ができます。

もともとNostrに限らずウェブアプリケーションとの連携をするために、WebLNという規格があります。簡単に言うと、ブラウザのグローバル領域を介して、LNウォレットの拡張機能と、タブで開いているウェブアプリが、お互いに連携するためのインターフェースを定めているものです。これに対応していると、LNによる支払いをウェブアプリが拡張機能に依頼できるようになります。さらにオプションで「確認無し」をオンにすると、拡張機能画面がポップアップせずにバックグラウンドで実行できるようになり、ノールック投げ銭ができるようになります。
似たようなものにNostrではNIP-07があります。NIP-07はNostrの秘密鍵を拡張機能に退避して、Nostrクライアントは秘密鍵を知らない状態で署名や複合を拡張機能に移譲できるようにしているものです。
Albyの拡張機能ではWebLNとNIP-07のどちらにも対応しています。
実はSnortはzapsが来る前からWebLNには対応していたのですが、さらに一歩進み、拡張機能ウォレットだけでなく、LNノードや拡張機能以外のLNウォレットと連携設定できるようになってきています。

umbrelなどでノードを立てている人ならLND with LNCでノードと直接繋げます。またLNDHubに対応したウォレットなどのアプリケーションとも繋げます。これらの接続は、WebLNにラップされて拡張機能ウォレットとインターフェースを揃えられた上で、Snort上でのインボイスの支払いに活用されます。
なお、LNCのpairingPhrase/passwordやLNDHubの接続情報などのクレデンシャルは、ブラウザのローカルストレージに保存されています。Nostrのリレーサーバなどには送られませんので、端末ごとに設定が必要です。
スマホアプリ
今回のメインです。なお、例によって(?)スペックは絶賛議論中でまだフィックスしていない中で記事を書いています。ディテールは変わるかもしれないので悪しからずです。
スマホアプリで上記のことをやるためには、後半のLNCやLNDHubはすでにzeusなどがやっているようにできますが、あくまでネイティブウォレットのラッパーです。Nostrでは限られた用途になるので1-click支払いのようなものを行うためにはそこから各スマホアプリが作り込む必要があります。まあこれはこれでやればいいという話でもあるのですが、LNノードやLNウォレットのアプリケーション側へのインターフェースの共通仕様は定められていないので、LNDとcore-lightningとeclairではすべて実装方法が違いますし、ウォレットもバラバラなので大変です。
そこで、多種多様なノードやウォレットの接続を取りまとめ一般アプリケーションへ統一したインターフェースを媒介するLN Adapter業界のリーディングカンパニーであるAlbyが動きました。AndroidアプリのAmethystで試験公開されていますが、スマホアプリでも上記のSnortのような連携が可能になるようなSDKが開発されました。
リリース記事 https://blog.getalby.com/native-zapping-in-amethyst/
"Unstoppable zapping for users"なんて段落見出しが付けられているように、スマホで別のアプリに切り替えてまた元に戻らなくても良いようにして、Nostr上でマイクロペイメントを滑らかにする、つまり、連打できることを繰り返し強調しています。
具体的にやっていることを見ていきます。以下の画像群はリリース記事の動画から抜粋しています。各投稿のzapsボタン⚡️をタップしたときの画面です。

上の赤枠が従来の投げ銭の詳細を決める場所で、下の赤枠の「Wallet Connect Service」が新たに追加されたAlby提供のSDKを用いたコネクト設定画面です。基本的にはOAuth2.0ベースのAlbyのAPIを活用していて、右上のAlbyアイコンをタップすると以下のようなOAuthの認可画面に飛びます。(ただし後述するように通常のOAuthとは一部異なります。)


画面デザインは違いますが、まあ他のアプリでよく目にするTwitter連携やGoogleアカウント連携とやっていることは同じです。
このOAuthベースのAPIはNostr専用のエンドポイントが建てられています。Nostr以外のECショップやマーケットプレイスなどへのAlbyのOAuthは汎用のエンドポイントが用意されています。よって通常のAlbyの設定とは別にセッション詳細を以下のサイトで作成する必要があります。
https://nwc.getalby.com/ (サブドメインのnwcはNostr Wallet Connectの略)
なぜNostrだけは特別なのかというところが完全には理解しきれていないですが、以下のところまで確認できています。一番にあるのは、Nostrクライアントにウォレットを組み込まずに、かつ、ノードやウォレットへの接続をNostrリレーサーバ以外は挟まずに"decentralized"にしたいというところだと理解しています。
- 上記のnwcのURLはalbyのカストディアルウォレットusername@getalby.comをNostrに繋ぐもの(たぶん)
- umbrelのLNノードを繋ぐためにはやはり専用のアプリがumbrelストアに上がっている。https://github.com/getAlby/umbrel-community-app-store
- 要するにOAuthの1stPartyの役割をウォレットやノードごとにそれぞれ建てる。
- OAuthのシークレットはクライアントに保存するので設定は各クライアント毎に必要。しかし使い回しすることは可能っぽい。通常のOAuthと異なり、1stParty側で3rdPartyのドメインはトラストしていないようなので。
- Nostrクライアントにウォレットを組み込まずに、さらにウォレットやノードへの接続をNostrリレーサーバ以外には挟まなくて良いようにするために、「NIP-47 Nostr Wallet Connect」というプロポーザルが起こされていて、絶賛議論中である。https://github.com/nostr-protocol/nips/pull/406
- このWallet Connect専用のアドホックなリレーサーバが建てられる。その情報が上記画像の赤枠の「Wallet Connect Service」の下半分のpub keyやらrelayURL。どうもNostrクライアントはNIP-47イベントについてはこのリレーサーバにしか送らないようにするらしい。(なんかNostrの基本設計を揺るがすユースケースの気がする...)
- Wallet Connect専用のNostrイベントでは、ペイメント情報をNostrアカウントと切り離すために、Nostrの秘密鍵とは別の秘密鍵が利用できるようにしている。
Imagin the Future
今回取り上げたNostrクライアントにウォレット接続を組み込む話を、Webのペイメントの歴史で類推してみましょう。
Snortでやっていることは、各サイトごとにクレジットカードを打ち込み各サイトがその情報を保持していたようなWeb1.0の時代に近いです。そうなるとクレジットカードの情報は各サービスごとに漏洩リスクなどがあり、Web1.0の時代はECが普及する壁の一つになっていました。(今でもAmazonなどの大手はそうですが)
Webではその後にPayPalをはじめとして、銀行口座やクレジットカードを各サイトから切り出して一括管理し、各ウェブサイトに支払いだけを連携するサービスが出てきて一般化しています。日本ではケータイのキャリア決済が利用者の心理的障壁を取り除きEC普及の後押しになりました。
後半のNostr Wallet ConnectはそれをNostrの中でやろうとしている試みになります。クレジットカードからLNに変える理由はビットコインの話になるので詳細は割愛しますが、現実世界の金(ゴールド)に類した価値保存や交換ができるインターネットマネーだからです。
とはいえ、Nostrの中だけならまだしも、これをNostr外のサービスで利用するためには、他のECショップやブログやSaaSがNostrを喋れる必要があります。そんな未来が来るわけないだろと思うかもしれませんが、言ってみればStripeはまさにそのようなサービスとなっていて、サイト内にクレジット決済のモジュールを組み込むための主流となっています。
果たして、Nostrを、他のECショップやブログやSaaSが喋るようになるのか!?
以上、「NostrはLNがWeb統合されマネーのインターネットプロトコルとしてのビットコインが本気出す具体行動のショーケースと見做せばOK」がお送りしました。
-
 @ e4950c93:1b99eccd
2025-04-30 09:27:09
@ e4950c93:1b99eccd
2025-04-30 09:27:09 -
 @ 3589b793:ad53847e
2025-04-30 12:10:06
@ 3589b793:ad53847e
2025-04-30 12:10:06前回の続きです。
特に「Snortで試験的にノート単位に投げ銭できる機能」について。実は記事書いた直後にリリースされて慌ててw追記してたんですが追い付かないということで別記事にしました。
今回のここがすごい!
「Snortで試験的にノート単位に投げ銭できる機能」では一つブレイクスルーが起こっています。それは「ウォレットにインボイスを放り投げた後に払い込み完了を提示できる」ようになったことです。これによりペイメントのライフサイクルが一通りカバーされたことになります。
Snortの画面

なにを当たり前のことをという向きもあるかもしれませんが、Nostrクライアントで払い込み完了を追跡することはとても難しいです。基本的にNostrとLNウォレットはまったく別のアプリケーションで両者の間を繋ぐのはインボイス文字列だけです。ウォレットもNostrからキックされずに、インボイス文字列をコピペするなりQRコードで読み取ったものを渡されるだけかもしれません。またその場でリアルタイムに処理される前提もありません。
なのでNostrクライアントでその後をトラックすることは難しく、これまではあくまで請求書を送付したり(LNインボイス)振り込み口座を提示する(LNアドレス)という一方的に放り投げてただけだったわけです。といっても魔法のようにNostrクライアントがトラックできるようになったわけではなく、今回の対応方法もインボイスを発行/お金を振り込まれるサービス側(LNURL)にNostrカスタマイズを入れさせるというものになります。
プロポーザルの概要について
前回の記事ではよくわからんで終わっていましたが、当日夜(日本時間)にスペックをまとめたプロポーザルも起こされました(早い!)。LNURLが、Nostr用のインボイスを発行して、さらにNostrイベントの発行を行っていることがポイントでした。名称は"Lightning Zaps"で確定のようです。プロポーザルは、NostrとLNURLの双方の発明者であるfiatjaf氏からツッコミが入り、またそれが妥当な指摘のために、エンドポイントURLのインターフェースなどは変わりそうなのですが、概要はそう変わらないだろうということで簡単にまとめてみます。
全体の流れ

図は、Nostrクライアント上に提示されているLNアドレスへ投げ銭が開始してから、Nostrクライアント上に払い込み完了したイベントが表示されるまでの流れを示しています。
- 投げ銭の内容が固まったらNostrイベントデータを添付してインボイスの発行を依頼する
- 説明欄にNostr用のデータを記載したインボイスを発行して返却する
- Nostrクライアントで提示されたインボイスをユーザーが何かしらの手段でウォレットに渡す
- ウォレットがLNに支払いを実行する
- インボイスの発行者であるLNURLが管理しているLNノードにsatoshiが届く
- LNURLサーバが投げ銭成功のNostrイベントを発行する
- Nostrクライアントがイベントを受信して投げ銭履歴を表示する
特にポイントとなるところを補足します。
対応しているLNアドレスの識別
LNアドレスに投げ銭する場合は、LNアドレスの有効状態やインボイス発行依頼する先の情報を
https://[domain]/.well-known/lnurlp/[username]から取得しています。そのレスポンス内容にNostr対応を示す情報を追加しています。ただし、ここに突っ込み入っていてlnurlp=LNURL Payから独立させるためにzaps専用のエンドポイントに変わりそうです。(2/15 追記 マージされましたが変更無しでした。PRのディスカッションが盛り上がっているので興味ある方は覗いてみてください。)インボイスの説明欄に書き込むNostrイベント(kind:9734)
これは投げ銭する側のNostrイベントです。投げ銭される者や対象ノートのIDや金額、そしてこのイベントを作成している者が投げ銭したということを「表明」するものになります。表明であって証明でないところは、インボイスを別の人が払っちゃう事態がありえるからですね。この内容をエンクリプトするパターンも用意されていたが複雑になり過ぎるという理由で今回は外され追加提案に回されました。また、このイベントはデータを作成しただけです。支払いを検知した後にLNURLが発行するイベントに添付されることになります。そのため投げ銭する者にちゃんと届くように作成者のリレーサーバリストも書き込まれています。
支払いを検知した後に発行するNostrイベント(kind:9735)
これが実際にNostrリレーサーバに発行されるイベントです。LNURL側はウォッチしているLNノードにsatoshiが届くと、インボイスの説明欄に書かれているNostrイベントを取り出して、いわば受領イベントを作成して発行します。以下のようにNostイベントのkind:9734とkind:9735が親子になったイベントとなります。
json { "pubkey": "LNURLが持っているNostrアカウントの公開鍵", "kind": 9735, "tags": [ [ "p", "投げ銭された者の公開鍵" ], [ "bolt11", "インボイスの文字列lnbc〜" ], [ "description", "投げ銭した者が作成したkind:9734のNostrイベント" ], [ "preimage", "インボイスのpreimage" ] ], }所感
とにかくNostrクライアントはLNノードを持たないしLNプロトコルとも直接喋らずにインボイス文字列だけで取り扱えるようになっているところがおもしろいと思っています。NostrとLNという二つのデセントライズドなオープンプロトコルが協調できていますし、前回も述べましたがどんなアプリでも簡単に真似できます。
とはいえ、さすがに払込完了のトラックは難しく、今回はLNURL側にそのすり合わせの責務が寄せられることになりました。しかし、LNURLもLNの上に作られたオープンプロトコル/スペックの位置付けになるため、他のLNURLのスペックに干渉するという懸念から、本提案のNIP-57に変更依頼が出されています。LN、LNURL、Nostrの3つのオープンプロトコルの責務分担が難しいですね。アーキテクチャ層のスタックにおいて3つの中ではNostrが一番上になるため、Nostrに相当するレイヤーの他のwebサービスでやるときはLNプロトコルを喋るなりLNノードを持つようにして、今回LNURLが寄せられた責務を吸収するのが無難かもしれません。
また、NIP-57の変更依頼理由の一つにはBOLT-12を見越した抽象化も挙げられています。他のLNURLのスペックを削ぎ落としてzapsだけにすることでBOLT-12にも載りやすくなるだろうと。LNURLの多くはBOLT-12に取り込まれる運命なわけですが、LNアドレス以外の点でもNostrではBOLT-12のOfferやInvoiceRequestのユースケースをやりたいという声が挙がっているため、NostrによりBOLT-12が進む展開もありそうだなあ、あってほしい。
-
 @ 3589b793:ad53847e
2025-04-30 12:02:13
@ 3589b793:ad53847e
2025-04-30 12:02:13※本記事は別サービスで2023年2月5日に公開した記事の移植です。
Nostrクライアントは多種ありますがメジャーなものはだいたいLNの支払いが用意されています。現時点でどんな組み込み方法になっているか調べました。この記事では主にSnortを対象にしています。
LN活用場面
大きくLNアドレスとLNインボイスの2つの形式があります。
1. LNアドレスで投げ銭をセットできる

LNURLのLNアドレスをセットすると、プロフィールやノート(ツイートに相当)からLN支払いができます。別クライアントのastralなどではプリミティブなLNURLの投げ銭形式
lnurl1dp68~でもセットできます。[追記]さらに本日、Snortで試験的にノート単位に投げ銭できる機能が追加されています。

2. LNインボイスが投稿できる

投稿でLNインボイスを貼り付ければ上記のように他の発言と同じようにタイムラインに流れます。Payボタンを押すと各自の端末にあるLNウォレットが立ち上がります。
3. DMでLNインボイスを送る
メッセージにLNインボイスが組み込まれているという点では2とほぼ同じですが、ユースケースが異なります。発表されたばかりですがリレーサーバの有料化が始まっていて、その決済をDMにLNインボイスを送付して行うことが試されています。2だとパブリックに投稿されますが、こちらはプライベートなので購入希望者のみにLNインボイスを届けられます。

おまけ: Nostrのユーザ名をLNアドレスと同じにする
直接は関係ないですが、Nostrはユーザー名をemail形式にすることができます。LNアドレスも自分でドメイン取って作れるのでNostrのユーザー名と投げ銭のアドレスを同じにできます。
LNウォレットのAlbyのドメインをNostrのユーザ名にも活用している様子 [Not found]
実装方法
LNアドレスもLNインボイスも非常にシンプルな話ですが軽くまとめます。 Snortリポジトリ
LNアドレス
- セットされたLNアドレスを分解して
https://[domain]/.well-known/lnurlp/[username]にリクエストする - 成功したら投げ銭量を決めるUIを提示する
- Get Inoviceボタンを押したら1のレスポンスにあるcallbackにリクエストしてインボイスを取得する
- 成功したらPayボタンを提示する
LNインボイス
- 投稿内容がLNインボイス識別子
lnbc10m〜だとわかると、識別子の中の文字列から情報(金額、説明、有効期限)を取り出し、表示用のUIを作成する - 有効期限内だったらPayボタンを提示し、期限が切れていたらExpiredでロックする
支払い
Payボタンを押された後の動きはアドレス、インボイスとも同じです。
- ブラウザでWebLN(Albyなど)がセットされていて、window.weblnオブジェクトがenableになっていると、拡張機能の支払い画面が立ち上がる。クライアント側で支払い成功をキャッチすることも可能。
- Open Walletボタンを押すと
lightning:lnbc10m~のURI形式でwindow.openされ、Mac/Windows/iPhone/Androidなど各OSに応じたアプリケーション呼び出しが行われ、URIに対応しているLNウォレットが立ち上がる
[追記]ノート単位の投げ銭
Snort周辺の数人(strike社員っぽい人が一人いて本件のメイン実装している)で試験的にやっているようで現時点では実装レベルでしか詳細わかりませんでした。strikeのzapといまいち区別が付かなかったのですが、実装を見るとnostrプロトコルにzapイベントが追加されています。ソースコメントではこの後NIP(nostr improvement proposal)が起こされるようでかなりハッキーです。zap=tipの方言なんでしょうか?
ノートやプロフィールやリアクションなどに加えて新たにnostrイベントに追加しているものは以下2つです。
- zapRequest 投げ銭した側が対象イベントIDと量を記録する
- zapReceipt 投げ銭を受け取った側用のイベント
一つでできそうと思ったけど、nostrは自己主権のプロトコルでイベント作成するには発行者の署名が必須なので2つに分かれているのでしょう。
所感
現状はクライアントだけで完結する非常にシンプルな方法になっています。リレーサーバも経由しないしクライアントにLNノードを組み込むこともしていません。サードパーティへのhttpリクエストやローカルのアプリに受け渡すだけなので、実はどんな一般アプリでもそんなに知識もコストも要らずにパッとできるものです。
現状ちょっと不便だなと思っていることは、タイムラインに流れるインボイスの有効期限内の支払い済みがわからないことです。Payボタンを押してエラーにならないとわかりません。ウォレットアプリに放り投げていてこのトレースするためには、ウォレット側で支払い成功したらNostrイベントを書き込むなどの対応しない限りは、サービス側でインボイスを定期的に一つ一つLNに投げてチェックするなどが必要だと思われるので、他のサービスでマネするときは留意しておくとよさそうです。
一方で、DMによるLNインボイス送付は活用方法が広がりそうな予感があります。Nostrの公開鍵による本人特定と、LNインボイスのメモ欄のテキスト情報による突き合わせだけでも、かんたんな決済機能として用いれそうだからです。もっとNostrに判断材料を追加したければイベント追加も簡単にできることをSnortが示しています。とくにリレーサーバ購読やPROメニューなどのNostr周辺の支払いはやりやすそうなので、DM活用ではなくなにかしらの決済メニューを搭載したNostrクライアントもすぐに出てきそう気がします。
- セットされたLNアドレスを分解して
-
 @ e4950c93:1b99eccd
2025-04-30 09:24:29
@ e4950c93:1b99eccd
2025-04-30 09:24:29 -
 @ 3589b793:ad53847e
2025-04-30 11:46:52
@ 3589b793:ad53847e
2025-04-30 11:46:52※本記事は別サービスで2022年9月25日に公開した記事の移植です。
LNの手数料の適正水準はどう見積もったらいいだろうか?ルーティングノードの収益性を算出するためにはどうアプローチすればよいだろうか?本記事ではルーティングノード運用のポジションに立ち参考になりそうな数値や計算式を整理する。
個人的な感想を先に書くと以下となる。
- 現在の手数料市場は収益性が低くもっと手数料が上がった方が健全である。
- 他の決済手段と比較すると、LN支払い料金は10000ppm(手数料1%相当)でも十分ではないか。4ホップとすると中間1ノードあたり2500ppmである。
- ルーティングノードの収益性を考えると、1000ppmあれば1BTC程度の資金で年利2.8%になり半年で初期費用回収できるので十分な投資対象になると考える。
基本概念の整理
LNの料金方式
- LNの手数料は送金額に応じた料率方式が主になる。(基本料金の設定もあるが1 ~ 0 satsが大半)
- 料率単位のppm(parts per million)は、1,000,000satsを送るときの手数料をsats金額で示したもの。
- %での手数料率に変換すると1000ppm = 0.1%になる。
- 支払い者が払う手数料はルーティングに参加した各ノードの手数料の合計である。本稿では4ホップ(経由ノードが4つ)のルーティングがあるとすれば、各ノードの取り分は単純計算で1/4とみなす。
- ルーティングノードの収益はアウトバウンドフローで発生するのでアウトバウンドキャパシティが直接的な収益資源となる。
LNの料金以外のベネフィット
本稿では料金比較だけを行うが実際の決済検討では以下のような料金以外の効用も忘れてはならない。
- Bitcoin(L1)に比べると、料金の安さだけでなく、即時確定やトランザクション量のスケールという利点がある。
- クレジットカードなどの集権サービスと比較した特徴はBitcoin(L1)とだいたい同じである。
- 24時間365日利用できる
- 誰でも自由に使える
- 信頼する第三者に対する加盟や審査や手数料率などの交渉手続きが要らない
- 検閲がなく匿名性が高い
- 逆にデメリットはオンライン前提がゆえの利用の不便さやセキュリティ面の不安さなどが挙げられる。
現在の料金相場
- ルーティングノードの料金設定
- sinkノードとのチャネルは500 ~ 1000ppmが多い。
- routing/sourceノードとのチャネルは0 ~ 100ppmあたりのレンジになる。
- リバランスする場合もsinkで収益を上げているならsink以下になるのが道理である。
- プロダクト/サービスのバックエンドにいるノードの料金設定
- sinkやsourceに相当するものは上記の通り。
- 1000〜5000ppmあたりで一律同じ設定というノードもよく見かける。
- ビジネスモデル次第で千差万別だがアクティブと思われるノードでそれ以上はあまり見かけない。
- 上記は1ノードあたりの料金になる。支払い全体では経由したノードの合計になる。
料金目安
いくつかの方法で参考数字を出していく。LN料金算出は「支払い全体/2ホップしたときの1ノードあたり/4ホップしたときの1ノードあたり」の三段階で出す。
類推方式
決済代行業者との比較
- Squareの加盟店手数料は、日本3.25%、アメリカ2.60%である。
- 参考資料 https://www.meti.go.jp/shingikai/mono_info_service/cashless_payment/pdf/20220318_1.pdf
3.25%とするとLNでは「支払い全体/2ホップしたときの1ノードあたり/4ホップしたときの1ノードあたり」でそれぞれ
32,500ppm/16,250ppm/8,125ppmになる。スマホのアプリストアとの比較
- Androidのアプリストアは年間売上高が100万USDまでなら15%、それ以上なら30%
- 参考資料https://support.google.com/googleplay/android-developer/answer/112622?hl=ja
15%とするとLNでは「支払い全体/2ホップしたときの1ノードあたり/4ホップしたときの1ノードあたり」でそれぞれ
150,000ppm/75,000ppm/37,500ppmになる。Bitcoin(L1)との比較
Bitcoin(L1)は送金額が異なっても手数料がほぼ同じため、従量課金のLNと単純比較はできない。そのためここではLNの方が料金がお得になる目安を出す。
Bitcoin(L1)の手数料設定
- SegWitのシンプルな送金を対象にする。
- input×1、output×2(送金+お釣り)、tx合計222byte
- L1の手数料は、1sat/byteなら222sats、10sat/byteなら2,220sats、100sat/byteなら22,200sats。(単純化のためvirtual byteではなくbyteで計算する)
- サンプル例 https://www.blockchain.com/btc/tx/15b959509dad5df0e38be2818d8ec74531198ca29ac205db5cceeb17177ff095
L1相場が1sat/byteの時にLNの方がお得なライン
- 100ppmなら、0.0222BTC(2,220,000sats)まで
- 1000ppmなら、0.00222BTC(222,000sats)まで
L1相場が10sat/byteの時にLNの方がお得なライン
- 100ppmなら、0.222BTC(22,200,000sats)まで
- 1000ppmなら、0.0222BTC(2,220,000sats)まで
L1相場が100sat/byteの時にLNの方がお得なライン
- 100ppmなら、2.22BTC(222,000,000sats)まで
- 1000ppmなら、0.222BTC(22,200,000sats)まで
コスト積み上げ方式
ルーティングノードの原価から損益分岐点となるppmを算出する。事業者ではなく個人を想定し、クラウドではなくラズベリーパイでのノード構築環境で計算する。
費用明細
- BTC市場価格 1sat = 0.03円(1BTC = 3百万円)
初期費用
- ハードウェア一式 40,000円
- Raspberry Pi 4 8GB
- SSD 1TB
- 外付けディスプレイ
- チャネル開設のオンチェーン手数料 6.69円/チャネル
- 開設料 223sats
- 223sats * BTC市場価格0.03円 = 6.69円
固定費用
- 電気代 291.6円/月
- 時間あたりの電力量 0.015kWh
- Raspberry Pi 4 電圧5V、推奨電源容量3.0A
- https://www.raspberrypi.com/documentation/computers/raspberry-pi.html#power-supply
- kWh単価27円
- 0.015kWh * kWh単価27円 * 1ヶ月の時間720h = 291.6円
損益分岐点
- 月あたりの電気代を上回るために9,720sats(291.6円)/月以上の収益が必要である。
- ハードウェア費用回収のために0.01333333BTC(133万sats) = 40,000円の収益が必要である。
費用回収シナリオ例
アウトバウンドキャパに1BTCをデポジットしたAさんを例にする。1BTCは初心者とは言えないと思うが、このくらい原資を用意しないと費用回収の話がしづらいという裏事情がある。チャネル選択やルーティング戦略は何もしていない仮定である。ノード運用次第であることは言うまでもないので今回は要素や式を洗い出すことが主目的で一つ一つの変数の値は参考までに。
変数設定
- インバウンドを同額用意して合計キャパを2BTCとする。
- 1チャネルあたり5m satsで40チャネル開設する。
- チャネル開設費用 223sats * 40チャネル = 8,920sats
- 初期費用合計 1,333,333sats + 8,920sats = 1,342,253sats
- 一回あたり平均ルーティング量 = 100,000sats
- 1チャネルあたり平均アウトバウンド数/日 = 2
- 1チャネルあたり平均アウトバウンドppm = 50
費用回収地点
- 1日のアウトバウンド量は、 40チャネル * 2本 * 100,000sats = 8m sats
- 手数料収入は、8m sats * 0.005%(50ppm) = 400sats/日。月換算すると12,000sats/月
- 電気代を差し引くと、12,000sats - 電気代9,720sats =月収益2,280sats(68.4円)
- 初期費用回収まで、1,342,253sats / 2,280sats = 589ヵ月(49年)
- 後述するが電気代差引き前で年利0.14%になる。
理想的なppm
6ヵ月での初期費用回収を目的にしてアウトバウンドppmを求める。
- ひと月あたり、初期費用合計1,342,253sats / 6ヵ月 + 電気代9,720sats = 233,429sats(7,003円)の収益が必要。
- 1日あたり、7,781sats(233円)の収益
- その場合の平均アウトバウンドppmは、 7,781sats(1日の収益量) / 8m sats(1日のアウトバウンド量) * 1m sats(ppm変換係数) = 973ppm
他のファイナンスとの比較
ルーティングノードを運用して手数料収入を得ることは資産運用と捉えることもできる。レンディングやトレードなどの他の資産運用手段とパフォーマンス比較をするなら、デポジットしたアウトバウンドキャパシティに対する手数料収入をAPY換算する。(獲得した手数料はアウトバウンドキャパシティに積み重ねられるので複利と見做せる)
例としてLNDg(v1.3.1)のAPY算出計算式を転載する。見ての通り画面上の表記はAPYなのに中身はAPRになっているので注意だが今回は考え方の参考としてこのまま採用する。
年換算 = 365 / 7 = 52.142857 年利 = (7dayの収益 * 年換算) / アウトバウンドのキャパシティ例えば上記のAさんの費用回収シナリオに当てはめると以下となる。
年利 0.14% = (400sats * 7日 * 年換算)/ 100m sats
電気代を差し引くと 76sats/日となり年利0.027%
もし平均アウトバウンド1000ppmになると8,000sats/日なので年利2.9%になる。 この場合、電気代はほぼ1日で回収されるため差し引いても大差なく7,676sats/日で年利2.8%になる。
考察
以上、BTC市場価格や一日のアウトバウンド量といった重要な数値をいくつか仮置きした上ではあるが、LN手数料の適正水準を考えるための参考材料を提示した。
まず、現在のLNの料金相場は他の決済手段から比べると圧倒的に安いことがわかった。1%でも競争力が十分ありそうなのに0.1%前後で送金することが大半である。
健全な市場発展のためには、ルーティングノードの採算が取れていることが欠かせないと考えるが、残念ながら現在の収益性は低い。ルーティングノードの収益性は仮定に仮定を重ねた見積もりになるが、平均アウトバウンドが1000ppmでようやく個人でも参入できるレベルになるという結論になった。ルーティングノードの立場に立つと、現在の市場平均から大幅な上昇が必要だと考える。
手数料市場は競争のためつねに下方圧力がかかっていて仕様上で可能な0に近づいている。この重力に逆らうためには、1. 需要 > 供給のバランスになること、2. 事業用途での高額買取のチャネルが増えること、の2つの観点を挙げる。1にせよ2にせよネットワークの活用が進むことで発生し、手数料市場の大きな変動機会になるのではないか。他の決済手段と比較すれば10000ppm、1チャネル2500ppmあたりまでは十分に健全な範囲だと考える。
-
 @ 6c67a3f3:b0ebd196
2025-04-30 08:40:15
@ 6c67a3f3:b0ebd196
2025-04-30 08:40:15To explore the link between Gavekal-style platform companies and the US dollar's status as the global reserve currency, we need to view the problem through multiple interlocking lenses—monetary economics, network effects, macro-political architecture, financial plumbing, and the logic of platform capitalism. Gavekal’s conceptual framework focuses heavily on capital-light, scalable businesses that act as platforms rather than traditional linear firms. Their model emphasizes "soft" balance sheets, asset-light capital formation, high intangible value creation, and the scaling of network effects. These traits dovetail in complex ways with the structural position of the United States in the global financial system.
What follows is a broad and recursive dissection of how these two phenomena—platform companies and reserve currency status—are mutually constitutive, each feeding the other, both directly and via second- and third-order effects.
- The Core Metaphor: Platforms and Monetary Hegemony
At its root, a platform is a meta-infrastructure—a set of protocols and affordances that enable others to interact, produce, consume, and transact. The dollar, as reserve currency, functions in an analogous way. It is not merely a medium of exchange but a platform for global commerce, pricing, credit formation, and risk transfer.
In this metaphor, the United States is not just a country but a platform operator of global finance. And like Amazon or Apple, it enforces terms of access, extracts rents, underwrites standardization, and benefits disproportionately from marginal activity across its ecosystem. Just as Apple's App Store tax or Amazon’s marketplace fee are invisible to most users, the dollar hegemon collects global seigniorage, institutional influence, and capital inflow not as overt tolls, but through the structuring of default behaviors.
This already suggests a deep isomorphism between platform logic and reserve currency logic.
- Capital-Light Scaffolding and Global Dollar Demand
Gavekal-style firms (e.g. Apple, Google, Microsoft) have something unusual in common: they generate high levels of free cash flow with low reinvestment needs. That is, they do not soak up global capital so much as recycle it outward, often via share buybacks or bond issuance. This creates a paradox: they are net issuers of dollar-denominated financial claims even as they are net accumulators of global income.
Now map this onto the structure of reserve currency systems. The US must export financial assets to the world (Treasuries, MBS, high-grade corporates) in order to satisfy foreign demand for dollar claims. But traditional exporting economies (e.g. Germany, China) create excess savings they must park in safe dollar assets, while running trade surpluses.
Gavekal-style firms allow the US to square a circle. The US economy does not need to run trade surpluses, because its platform companies export “intangible products” at near-zero marginal cost (e.g. iOS, search ads, cloud infrastructure), generate global rents, and then repatriate those earnings into US financial markets. These flows offset the US current account deficit, plugging the "Triffin dilemma" (the need to run deficits to supply dollars while maintaining credibility).
Thus, platform companies act as soft exporters, replacing industrial exports with intangible, rent-generating capital. Their global cash flows are then recycled through dollar-denominated assets, providing the scale and liquidity necessary to sustain reserve status.
- The Hierarchy of Money and Intangible Collateral
Modern monetary systems rest on a hierarchy of collateral—some assets are more money-like than others. US Treasuries sit at the apex, but AAA-rated corporates, especially those with global footprints and balance-sheet integrity, are close behind.
Platform firms are unique in their capacity to create high-quality, globally accepted private collateral. Apple’s bonds, Microsoft’s equity, and Google’s cash reserves function as synthetic dollar instruments, widely accepted, liquid, and backed by consistent income streams. These firms extend the reach of the dollar system by providing dollar-denominated assets outside the banking system proper, further embedding dollar logic into global capital flows.
Moreover, platform companies often internalize global tax arbitrage, holding cash offshore (or in tax-efficient jurisdictions) and issuing debt domestically. This creates a loop where foreign dollar claims are used to finance US domestic consumption or investment, but the underlying income comes from global activities. This is reverse colonization through intangibles.
- Winner-Take-Most Dynamics and Network Effects in Dollar Space
The dollar system, like platform capitalism, obeys a power-law distribution. Liquidity begets liquidity. The more that dollar instruments dominate global trade, the more pricing, settlement, and hedging mechanisms are built around them. This self-reinforcing loop mimics network effect entrenchment: the more users a platform has, the harder it is to displace.
Reserve currency status is not a product of GDP share alone. It’s a function of infrastructure, institutional depth, legal recourse, capital mobility, and networked habits. Likewise, Apple’s dominance is not just about better phones, but about developer lock-in, payment systems, user base, and design mores.
Gavekal-style firms reinforce this pattern: their software platforms often denominate activity in dollars, price in dollars, store value in dollars, and link digital labor across borders into dollar-based flows. YouTube creators in Jakarta are paid in dollars. AWS charges Chilean entrepreneurs in dollars. App Store remittances to Kenya settle in dollars.
This creates global micro-tributaries of dollar flows, all of which aggregate into the larger river that sustains dollar supremacy.
- Geopolitical Power Projection by Private Means
Traditional hegemonic systems project power through military, legal, and diplomatic tools. But platforms provide soft control mechanisms. The US can influence foreign populations and elite behavior not merely through embassies and aircraft carriers, but through tech platforms that shape discourse, information flows, norms, and cognitive frames.
This is a kind of cognitive imperialism, in which reserve currency status is bolstered by the fact that cultural products (e.g. Netflix, social media, productivity tools) are encoded in American norms, embedded in American legal systems, and paid for in American currency.
The platform firm thus becomes a shadow extension of statecraft, whether or not it sees itself that way. Dollar hegemony is reinforced not only by Treasury markets and SWIFT access, but by the gravity of the mental ecosystem within which the global bourgeoisie operates. To earn, spend, invest, create, and dream within American-built systems is to keep the dollar central by default.
- Second-Order Effects: The Intangibility Ratchet and Global Liquidity Traps
An overlooked consequence of Gavekal-style platform dominance is that global capital formation becomes disembodied. That is, tangible projects—factories, infrastructure, energy systems—become less attractive relative to financial or intangible investments.
As a result, much of the world, especially the Global South, becomes capital-starved even as capital is abundant. Why? Because the returns on tangible investment are less scalable, less defensible, and less liquid than buying FAANG stocks or US Treasuries.
This results in a liquidity trap at the global scale: too much capital chasing too few safe assets, which only reinforces demand for dollar instruments. Meanwhile, intangible-intensive firms deepen their moats by mining attention, user data, and payment flows—often without any large-scale employment or industrial externalities.
Thus, Gavekal-style firms create asymmetric global development, further concentrating economic gravitational mass in the dollar zone.
- Feedback Loops and Fragility
All of this breeds both strength and fragility. On one hand, platform firm cash flows make the dollar system seem robust—anchored in cash-generative monopolies with global reach. On the other hand, the system becomes narrower and more brittle. When so much of global liquidity is intermediated through a few firms and the sovereign system that hosts them, any attack on these nodes—financial, legal, technological, or geopolitical—could unseat the equilibrium.
Moreover, platform logic tends to reduce systemic redundancy. It optimizes for efficiency, not resilience. It centralizes control, narrows option sets, and abstracts real production into code. If the dollar system ever loses credibility—through inflation, sanctions overreach, geopolitical backlash, or platform fatigue—the network effects could reverse violently.
- Conclusion: The Intangible Empire
The United States today operates an empire of intangibles, in which reserve currency status and platform firm dominance are co-constituted phenomena. Each reinforces the other:
Platform firms channel global rents into dollar instruments.
The dollar system provides legal scaffolding, liquidity, and pricing infrastructure for these firms.
Global user bases are conditioned into dollar-denominated interaction by default.
Financial markets treat platform firms as synthetic sovereigns: safe, liquid, predictable.
What is left is a cybernetic loop of financialized cognition: the dollar is strong because platform firms dominate, and platform firms dominate because the dollar is strong.
This loop may persist longer than many expect, but it is not permanent. Its unravelling, when it comes, will likely not be driven by any single actor, but by the erosion of symbolic power, the emergence of parallel platforms, or the ecological unsustainability of the model. But for now, the Gavekal firm and the dollar empire are the two poles of a single global architecture—seen best not as cause and effect, but as the two faces of the same Janus coin.
-
 @ edeb837b:ac664163
2025-04-30 07:25:41
@ edeb837b:ac664163
2025-04-30 07:25:41We’re incredibly proud to announce that NVSTly has won the Gold Stevie® Award for Tech Startup of the Year – Services in the 23rd Annual American Business Awards®! Winners were officially revealed on April 24th, and this recognition is a powerful validation of the innovation, impact, and passion our team continues to deliver every day.
More than 250 professionals worldwide participated in the judging process to select this year’s Stevie Award winners.
We were honored among a competitive field of over 3,600 nominations from organizations across nearly every industry. NVSTly was recognized for redefining social investing with a first-of-its-kind platform that empowers traders to track, share, and automatically broadcast trades and buy/sell alerts across nearly every financial market—including stocks, options, forex, and crypto—with futures support coming soon.
The Stevie judges praised NVSTly for “creating an ecosystem that blends brokerage integration, real-time trade tracking, and community engagement into one seamless experience,” and noted that “NVSTly’s social investing model is paving the way for a new generation of retail traders.”
This award comes at a time of major momentum for us:
:star: 4.9-star rating on the iOS App Store :star: 5.0-star rating on Google Play :star: 4.9-star rating on Product Hunt :star: 5.0-star rating on Disboard for our 51,000+ strong Discord trading community :star: 4.98-star rating on Top.gg — making our trading bot the highest-rated and only one of its kind in the finance category
And it’s not our first recognition. NVSTly has previously earned:
:trophy: Fintech Product of the Week on Product Hunt (2023 & 2024) :trophy: People’s Choice Award at the 2024 Benzinga Fintech Awards
We’re still just getting started. Our mobile and web platform is used by over 10,000 traders, and our brokerage integrations now include Webull, with Moomoo support launching in the coming days and Schwab integration already underway. These integrations allow traders to automate buy/sell alerts directly to their NVSTly followers and across Discord and supported social platforms.
“Winning a Gold Stevie is an incredible milestone that reflects the hard work of our team and the unwavering support of our community,” said Rich Watson, CEO of NVSTly. “We’ve always believed that trading should be transparent, collaborative, and empowering—and this recognition confirms we’re building something truly impactful.”
More than 3,600 nominations from organizations of all sizes and in virtually every industry were submitted this year for consideration in a wide range of categories, including Startup of the Year, Executive of the Year, Best New Product or Service of the Year, Marketing Campaign of the Year, Thought Leader of the Year, and App of the Year, among others. NVSTly was nominated in the Tech Startup of the Year – Services category for financial technology startups.
We’ll be officially celebrated at the 2025 Stevie Awards gala in New York City on June 10, but today, we’re celebrating with the traders, creators, investors, and builders who have believed in our mission from day one. (It's still undecided if anyone representing NVSTly will attend the award event to be presented or award.)
Thank you for being part of this journey. We’re just getting started.
-
 @ 3589b793:ad53847e
2025-04-30 10:53:29
@ 3589b793:ad53847e
2025-04-30 10:53:29※本記事は別サービスで2022年5月22日に公開した記事の移植です。
Happy 🍕 Day's Present
まだ邦訳版が出版されていませんがこれまでのシリーズと同じくGitHubにソースコードが公開されています。なんと、現在のライセンスでは個人使用限定なら翻訳や製本が可能です。Macで、翻訳にはPDFをインプットにできるDeepLを用いた環境で、インスタントに製本してKindleなどで読めるようにする方法をまとめました。
手順の概要
- Ruby環境を用意する
- PDF作成ツールをセットアップする
- GitHubのリポジトリを自分のPCにクローンする
- asciidocをPDFに変換する
- DeepLを節約するためにPDFを結合する
- DeepLで翻訳ファイルを作る
- 一冊に製本する
この手法の強み・弱み
翻訳だけならPDFを挟まなくてもGithubなどでプレビューできるコンパイル後のドキュメントの文章をコピーしてDeepLのWebツールにペーストすればよいですが、原著のペーパーブックで438ページある大容量です。熟練のコピペ職人でも年貢を納めて後進(機械やソフトウェア)に道を譲る刻ではないでしょうか?ただし、Pros/Consがあります。
Pros
- 一冊の本になるので毎度のコピペ作業がいらない
- Pizzaを食べながらタブレットやKindleで読める
- 図や表が欠落しない(プロトコルの手順を追った解説が多いため最大の動機でした)
- 2022/6/16追記: DeepLの拡張機能がアップデートされウェブページの丸ごと翻訳が可能になりました。よってウェブ上のgithubの図表付きページをそのまま翻訳できます。
Cons
- Money is power(大容量のためDeepLの有料契約が必要)
- ページを跨いだ文章が統合されずに不自然な翻訳になる(仕様です)
- ~~翻訳できない章が一つある(解決方法がないか調査中です。DeepLさんもっとエラーメッセージ出してくれ。Help me)~~ DeepLサポートに投げたら翻訳できるようになりました。
詳細ステップ
0.Ruby環境を用意する
asciidoctorも新しく入れるなら最新のビルドで良いでしょう。
1.PDF作成ツールをセットアップする
$ gem install asciidoctor asciidoctor-pdf $ brew install gs2.GitHubのリポジトリを自分のPCにクローンする
どこかの作業ディレクトリで以下を実行する
$ git clone git@github.com:lnbook/lnbook.git $ cd lnbook3.asciidocをPDFに変換する
ワイルドカードを用いて本文を根こそぎPDF化します。
$ asciidoctor-pdf 0*.asciidoc 1*.asciidocいろいろ解析の警告が出ますが、ソースのasciidocを弄んでいくなりawsomeライブラリを導入すれば解消できるはずです。しかし如何せん量が多いので心が折れます。いったん無視して"Done is better than perfect"精神で最後までやり切りましょう。そのままGO!
また、お好みに合わせて、htmlで用意されている装丁用の部品も準備しましょう。私は表紙のcover.htmlをピックしました。ソースがhtmlなのでasciidoctorを通さず普通にPDFへ変換します。https://qiita.com/chenglin/items/9c4ed0dd626234b71a2c
4.DeepLを節約するためにPDFを結合する
DeepLでは課金プラン毎に翻訳可能なファイル数が設定されている上に、一本あたりの最大ファイルサイズが10MBです。また、翻訳エラーになる章が含まれていると丸ごとコケます。そのためPDCAサイクルを回し、最適なファイル数を手探りで見つけます。以下が今回導出した解となります。
$ gs -q -dNOPAUSE -dBATCH -sDEVICE=pdfwrite -sOutputFile=output_1.pdf 01_introduction.pdf 02_getting_started.pdf 03_how_ln_works.pdf 04_node_client.pdf 05_node_operations.pdf$gs -q -dNOPAUSE -dBATCH -sDEVICE=pdfwrite -sOutputFile=output_2_1.pdf 06_lightning_architecture.pdf 07_payment_channels.pdf 08_routing_htlcs.pdf$gs -q -dNOPAUSE -dBATCH -sDEVICE=pdfwrite -sOutputFile=output_2_2.pdf 09_channel_operation.pdf 10_onion_routing.asciidoc$ gs -q -dNOPAUSE -dBATCH -sDEVICE=pdfwrite -sOutputFile=output_3.pdf 11_gossip_channel_graph.pdf 12_path_finding.pdf 13_wire_protocol.pdf 14_encrypted_transport.pdf 15_payment_requests.pdf 16_security_privacy_ln.pdf 17_conclusion.pdf5. DeepLで翻訳ファイルを作る
PDFファイルを真心を込めた手作業で一つ一つDeepLにアップロードしていき翻訳ファイルを作ります。ファイル名はデフォルトの
[originalName](日本語).pdfのままにしています。6. 一冊に製本する
表紙 + 本文で作成する例です。
$ gs -q -dNOPAUSE -dBATCH -sDEVICE=pdfwrite -sOutputFile=mastering_ln_jp.pdf cover.pdf "output_1 (日本語).pdf" "output_2_1 (日本語).pdf" "output_2_2 (日本語).pdf" "output_3 (日本語).pdf"コングラチュレーションズ🎉

あなたは『Mastering the Lightning Network』の日本語版を手に入れた!個人使用に限り、あとは煮るなり焼くなりEPUBなりkindleへ送信するなり好き放題だ。
-
 @ 4e616576:43c4fee8
2025-04-30 09:57:29
@ 4e616576:43c4fee8
2025-04-30 09:57:29asdf
-
 @ d08c9312:73efcc9f
2025-04-30 09:59:52
@ d08c9312:73efcc9f
2025-04-30 09:59:52Resolvr CEO, Aaron Daniel, summarizes his keynote speech from the Bitcoin Insurance Summit, April 26, 2025
Introduction
At the inaugural Bitcoin Insurance Summit in Miami, I had the pleasure of sharing two historical parallels that illuminate why "Bitcoin needs insurance, and insurance needs Bitcoin." The insurance industry's reactions to fire and coffee can help us better understand the profound relationship between emerging technologies, risk management, and commercial innovation.
Fire: Why Bitcoin Needs Insurance
The first story explores how the insurance industry's response to catastrophic urban fires shaped modern building safety. Following devastating events like the Great Fire of London (1666) and the Great Chicago Fire (1871), the nascent insurance industry began engaging with fire risk systematically.
Initially, insurers offered private fire brigades to policyholders who displayed their company's fire mark on their buildings. This evolved into increasingly sophisticated risk assessment and pricing models throughout the 19th century:
- Early 19th century: Basic risk classifications with simple underwriting based on rules of thumb
- Mid-19th century: Detailed construction types and cooperative sharing of loss data through trade associations
- Late 19th/Early 20th century: Scientific, data-driven approaches with differentiated rate pricing
The insurance industry fundamentally transformed building construction practices by developing evidence-based standards that would later inform regulatory frameworks. Organizations like the National Board of Fire Underwriters (founded 1866) and Underwriters Laboratories (established 1894) tested and standardized new technologies, turning seemingly risky innovations like electricity into safer, controlled advancements.
This pattern offers a powerful precedent for Bitcoin. Like electricity, Bitcoin represents a new technology that appears inherently risky but has tremendous potential for society. By engaging with Bitcoin rather than avoiding it, the insurance industry can develop evidence-based standards, implement proper controls, and ultimately make the entire Bitcoin ecosystem safer and more robust.
Coffee: Why Insurance Needs Bitcoin
The second story reveals how coffee houses in 17th-century England became commercial hubs that gave birth to modern insurance. Nathaniel Canopius brewed the first documented cup of coffee in England in 1637. But it wasn't until advances in navigation and shipping technology opened new trade lanes that coffee became truly ubiquitous in England. Once global trade blossomed, coffee houses rapidly spread throughout London, becoming centers of business, information exchange, and innovation.
In 1686, Edward Lloyd opened his coffee house catering to sailors, merchants, and shipowners, which would eventually evolve into Lloyd's of London. Similarly, Jonathan's Coffee House became the birthplace of what would become the London Stock Exchange.
These coffee houses functioned as information networks where merchants could access shipping news and trade opportunities, as well as risk management solutions. They created a virtuous cycle: better shipping technology brought more coffee, which fueled commerce and led to better marine insurance and financing, which in turn improved global trade.
Today, we're experiencing a similar technological and financial revolution with Bitcoin. This digital, programmable money moves at the speed of light and operates 24/7 as a nearly $2 trillion asset class. The insurance industry stands to benefit tremendously by embracing this innovation early.
Conclusion
The lessons from history are clear. Just as the insurance industry drove safety improvements by engaging with fire risk, it can help develop standards and best practices for Bitcoin security. And just as coffee houses created commercial networks that revolutionized finance, insurance, and trade, Bitcoin offers new pathways for global commerce and risk management.
For the insurance industry to remain relevant in a rapidly digitizing world, it must engage with Bitcoin rather than avoid it. The companies that recognize this opportunity first will enjoy significant advantages, while those who resist change risk being left behind.
The Bitcoin Insurance Summit represented an important first step in creating the collaborative spaces needed for this transformation—a modern version of those innovative coffee houses that changed the world over three centuries ago.
View Aaron's full keynote:
https://youtu.be/eIjT1H2XuCU
For more information about how Resolvr can help your organization leverage Bitcoin in its operations, contact us today.
-
 @ 4e616576:43c4fee8
2025-04-30 09:48:05
@ 4e616576:43c4fee8
2025-04-30 09:48:05asdfasdflkjasdf
-
 @ 4e616576:43c4fee8
2025-04-30 09:42:33
@ 4e616576:43c4fee8
2025-04-30 09:42:33lorem ipsum
-
 @ 8d34bd24:414be32b
2025-04-30 04:55:06
@ 8d34bd24:414be32b
2025-04-30 04:55:06My post on the signs of the End Times according to Jesus got way too long. It was too long to email, so I had to split it into two posts. I recommend reading Part 1 before continuing. You also may want to read my post Signs of the Times: Can We Know? I also want to reiterate my caveat. Although I believe the signs suggests the Rapture and the Tribulation are coming soon, no one can know the exact hour or day, so I can’t say exactly what soon means (days, months, years, decades, or possibly more).
As a review here is the primary passage where Jesus answers His disciples’ question “What will be the sign of Your coming, and of the end of the age?” Below the passage is the 8 signs He gave. We will pick up with point 5.
Jesus’s Signs of the End
As He was sitting on the Mount of Olives, the disciples came to Him privately, saying, “Tell us, when will these things happen, and what will be the sign of Your coming, and of the end of the age?”
And Jesus answered and said to them, “See to it that no one misleads you. For many will come in My name, saying, ‘I am the Christ,’ and will mislead many. You will be hearing of wars and rumors of wars. See that you are not frightened, for those things must take place, but that is not yet the end. For nation will rise against nation, and kingdom against kingdom, and in various places there will be famines and earthquakes. But all these things are merely the beginning of birth pangs.
“Then they will deliver you to tribulation, and will kill you, and you will be hated by all nations because of My name. At that time many will fall away and will betray one another and hate one another. Many false prophets will arise and will mislead many. Because lawlessness is increased, most people’s love will grow cold. But the one who endures to the end, he will be saved. This gospel of the kingdom shall be preached in the whole world as a testimony to all the nations, and then the end will come. (Matthew 24:3-14) {emphasis mine}
Here is my summary of the signs Jesus said would identify the coming of the 7 year Tribulation:
-
Wars and rumors of wars. (Matthew 24:6a)
-
Famines (Matthew 24:7)
-
Earthquakes (Matthew 24:7).
-
Israel will be attacked and will be hated by all nations (Matthew 24:9)
-
Falling away from Jesus (Matthew 24:10)
-
Many Misled (Matthew 24:10)
-
People’s love will grow cold (Matthew 24:12)
-
Gospel will be preached to the whole world (Matthew 24:14)
The first 4 signs relate more to physical and political signs that the end times are near. The last 4 signs relate to spiritual matters.
5. Falling away from Jesus
One thing we are definitely seeing today is a falling away. This is most prevalent in the historically Christian Western nations in Europe and North America (and to a lesser, but significant, extent South America).
But the Spirit explicitly says that in later times some will fall away from the faith, paying attention to deceitful spirits and doctrines of demons, by means of the hypocrisy of liars seared in their own conscience as with a branding iron, men who forbid marriage and advocate abstaining from foods which God has created to be gratefully shared in by those who believe and know the truth. (1 Timothy 4:1-3) {emphasis mine}
For centuries Europe and North America were full of Christians or at least cultural Christians. Today that is no longer true. Christians are even being considered the hateful, criminal class and things like praying outside an abortion clinic is being punished with jail time. The Western nations can no longer be called Christian nations.
There are still a relatively large number of Americans who call themselves Christians, but the majority do not have a biblical worldview or live lives more like Christ than non-Christians.
“Seven out of 10 US adults call themselves “Christians” and yet only 6 in 100 (6%) actually have a biblical worldview.” In general, most Christian’s worldview does not align with the Bible, according to George Barna Surveys. In the most recent survey they found:
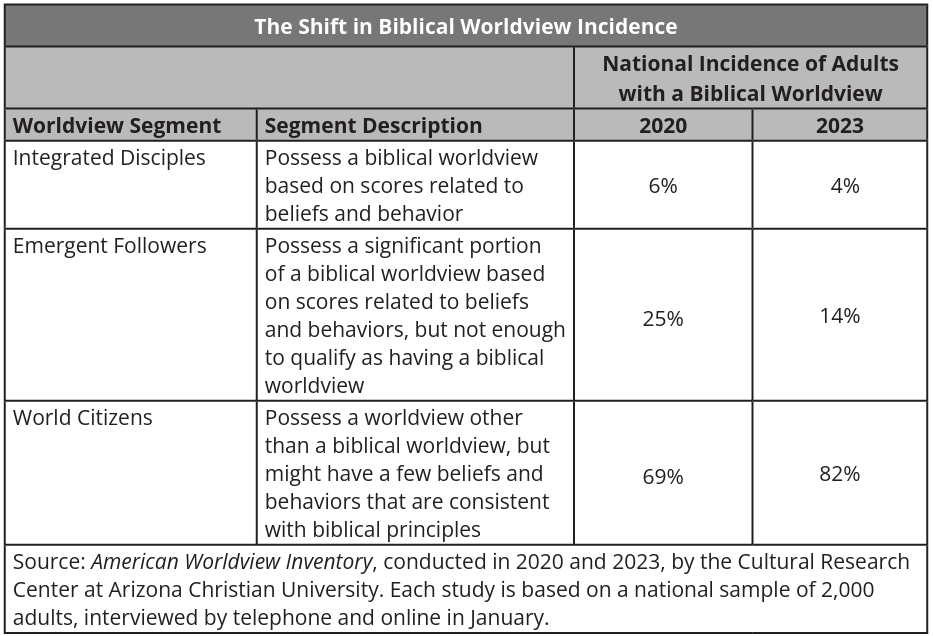 Many self-proclaimed Christians tend to believe a form of syncretism where they combine certain biblical principles with cultural ideas, scientism, and other religions to make “Christianity” into whatever they want to believe, just as the Bible predicted almost 2,000 years ago.
Many self-proclaimed Christians tend to believe a form of syncretism where they combine certain biblical principles with cultural ideas, scientism, and other religions to make “Christianity” into whatever they want to believe, just as the Bible predicted almost 2,000 years ago.I solemnly charge you in the presence of God and of Christ Jesus, who is to judge the living and the dead, and by His appearing and His kingdom: preach the word; be ready in season and out of season; reprove, rebuke, exhort, with great patience and instruction. For the time will come when they will not endure sound doctrine; but wanting to have their ears tickled, they will accumulate for themselves teachers in accordance to their own desires, and will turn away their ears from the truth and will turn aside to myths. (2 Timothy 4:1-4) {emphasis mine}
This is both a sign of the end times and something to watch in our own lives. I pray you will analyze your own life and beliefs in the light of the Bible to make sure you aren’t integrating unbiblical principles into your worldview.
6. Many Misled
Closely related to the falling away is that many will be misled. We have reached the point that the majority of so-called churches teach ideas and principles contrary to the Bible. They focus more on entertainment, self-help, and making everyone feel good about themselves instead of teaching of sin and the need for forgiveness or teaching how to live lives honoring to Christ. Preaching obedience to God has become anathema in most churches.
I am amazed that you are so quickly deserting Him who called you by the grace of Christ, for a different gospel; which is really not another; only there are some who are disturbing you and want to distort the gospel of Christ. But even if we, or an angel from heaven, should preach to you a gospel contrary to what we have preached to you, he is to be accursed! As we have said before, so I say again now, if any man is preaching to you a gospel contrary to what you received, he is to be accursed! (Galatians 1:6-9) {emphasis mine}
We are also lied to and/or misled by politicians, scientists, the media, and the culture in general. We are told that science has disproven the Bible, despite the fact that nothing of the sort has occurred. (See my series on a literal Genesis for some details. icr.org and aig.org are also good resources). Peter warned of this very view.
Know this first of all, that in the last days mockers will come with their mocking, following after their own lusts, and saying, “Where is the promise of His coming? For ever since the fathers fell asleep, all continues just as it was from the beginning of creation.” For when they maintain this, it escapes their notice that by the word of God the heavens existed long ago and the earth was formed out of water and by water, through which the world at that time was destroyed, being flooded with water. But by His word the present heavens and earth are being reserved for fire, kept for the day of judgment and destruction of ungodly men. (2 Peter 3:3-7) {emphasis mine}
God warned us that the last days would be far enough into the future that people would begin to mock the coming of the Tribulation & Millennium and deny the clear truths spoken of in the Bible. We are seeing this everywhere today.
We are also warned to be alert to deception so we, believers, are not misled.
Now we request you, brethren, with regard to the coming of our Lord Jesus Christ and our gathering together to Him, that you not be quickly shaken from your composure or be disturbed either by a spirit or a message or a letter as if from us, to the effect that the day of the Lord has come. Let no one in any way deceive you, for it will not come unless the apostasy comes first, and the man of lawlessness is revealed, the son of destruction, who opposes and exalts himself above every so-called god or object of worship, so that he takes his seat in the temple of God, displaying himself as being God. (2 Thessalonians 2:1-4) {emphasis mine}
7. People’s love will grow cold
You can feel love growing cold day by day. We no longer have community that works together, but have been broken into groups to fight against one another. Instead of friendly, logical debate with those with whom we disagree, we have name calling, hate, and even violence. Children have been taught to hate their parents and parents have been taught to not value children and to murder them for convenience. The church has been split into so many different denominations that I don’t know if it is possible to know what they all are and many are fighting in hateful manner against each other. Hate, depression, and selfishness seem to have taken over the world.
But realize this, that in the last days difficult times will come. For men will be lovers of self, lovers of money, boastful, arrogant, revilers, disobedient to parents, ungrateful, unholy, unloving, irreconcilable, malicious gossips, without self-control, brutal, haters of good, treacherous, reckless, conceited, lovers of pleasure rather than lovers of God, holding to a form of godliness, although they have denied its power; Avoid such men as these. (2 Timothy 3:1-5) {emphasis mine}
Yes, spiritually and physically we are a basket case and it feels like the world is literally falling apart around us. This was predicted almost 2,000 years ago and is all according to God’s perfect plan. Most people turn to God in hard times and we have those in abundance. We do not need to despair, but need to turn to God and lean on Him for wisdom, faith, and peace. This is the birth pangs before the Tribulation and the Second coming of Jesus Christ. The news isn’t all bad, though.
8. Gospel preached to the whole world
The really good news is that the Gospel is being preached around the world. Parts of the world that had never heard the Gospel are hearing it and turning to Jesus.
All the ends of the earth will remember and turn to the Lord , And all the families of the nations will worship before You. (Psalm 22:27) {emphasis mine}
Wycliffe Bible translators is hoping to have at least started Bible translation in every active language by the end of this year (2025)
He says, “It is too small a thing that You should be My Servant To raise up the tribes of Jacob and to restore the preserved ones of Israel; I will also make You a light of the nations So that My salvation may reach to the end of the earth.” (Isaiah 49:6) {emphasis mine}
The Joshua Project tracks nations and people groups to determine which have been reached and which have not. It still looks like there is a large portion of the population that has not received the Gospel, but I also know people who are or have shared the Gospel to some of these people, so this map doesn’t mean that there are no Christians or that the Gospel has not been shared at all, but it does mean many people in these areas have not heard the Gospel and/or, that due to hatred of Christians, it is dangerous to share the Gospel and therefore has to be done slowly, carefully, and privately. Most of these unreached or barely reached people groups are areas that are predominantly Muslim, where those preaching the Gospel or those converting to Christianity are at risk of jail or death sentences.
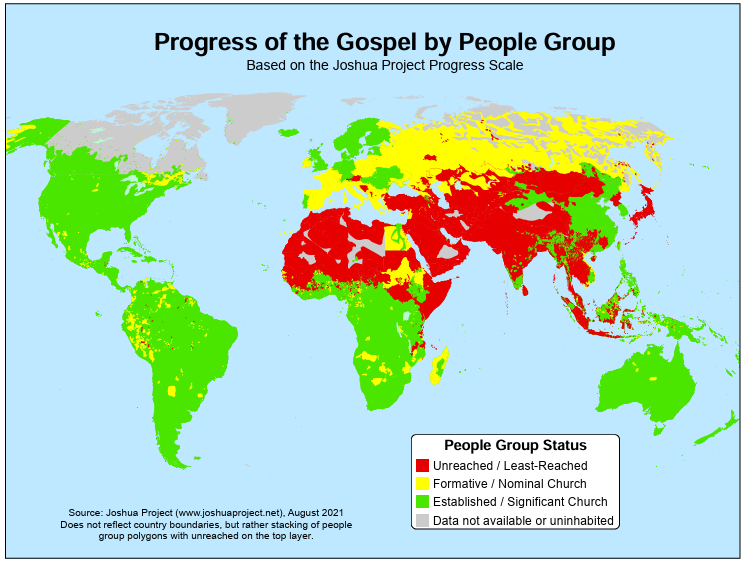 As you can see, everything that Jesus said would come before the end is either escalating or here. We need to be ready and work to bring as many people to Christ as possible while we still have the opportunity because Jesus could come for us at any moment.
As you can see, everything that Jesus said would come before the end is either escalating or here. We need to be ready and work to bring as many people to Christ as possible while we still have the opportunity because Jesus could come for us at any moment.Share the Gospel with all those around you. Consider supporting missionaries, especially those going to unreached/least-reached areas. Maybe even consider becoming a missionary yourself. The harvest is plentiful, but the workers are few.
May the God of heaven give us a heart for the lost around the world. May He give us the courage to share the Gospel with all those around us. May He align our priorities with His priorities, so we can be useful tools in the hands of God almighty.
Trust Jesus.
FYI, I hope to write several more articles on the end times (signs of the times, the rapture, the millennium, and the judgement), but I might be a bit slow rolling them out because I want to make sure they are accurate and well supported by Scripture. You can see my previous posts on the end times on the end times tab at trustjesus.substack.com. I also frequently will list upcoming posts.
-
-
 @ c1e6505c:02b3157e
2025-04-30 02:50:55
@ c1e6505c:02b3157e
2025-04-30 02:50:55Photography, to me, is a game - a game of snatching absurd, beautiful, fleeting moments from life. Anything staged or overly polished falls into what Garry Winogrand nails as “illustration work.” I’m with him on that. Photography is about staying awake to the world, to the “physical reality” or circumstances we’re steeped in, and burning that light onto film emulsion (or pixels now), locking a moment into matter forever. It’s not like painting, where brushstrokes mimic what’s seen, felt, or imagined. Photography captures photons - light itself - and turns it into something tangible. The camera, honestly, doesn’t get enough credit for being such a wild invention.
Lately, I’ve been chewing on what to do with a batch of new photos I’ve shot over the past month, which includes photographs from a film project, a trip to Manhattan and photos of David Byrne (more on that in another post). Maybe it's another photo-zine that I should make. It’s been a minute since my last one, Hiding in Hudson (https://www.youtube.com/watch?v=O7_t0OldrTk&t=339s). Putting out printed work like zines or books is killer practice — it forces you to sharpen your compositions, your vision, your whole deal as a photographer. Proof of work, you know?
This leads to a question: anyone out there down to help or collab on printing a photo-zine? I’d love to keep it DIY, steering clear of big companies.
In the spirit of getting back into a rhythm of daily shooting, here are a few recent shots from the past few days. Just wandering aimlessly around my neighborhood — bike rides, grocery runs, wherever I end up.
Camera used: Leica M262
Edited with: Lightroom + Dehancer Film
*Support my work and the funding for my new zine by sending a few sats: colincz@getalby.com *






-
 @ 99895004:c239f905
2025-04-30 01:43:05
@ 99895004:c239f905
2025-04-30 01:43:05 Yes, FINALLY, we are extremely excited to announce support for nostr.build (blossom.band) on Primal! Decades in the making, billions of people have been waiting, and now it’s available! But it’s not just any integration, it is the next level of decentralized media hosting for Nostr. Let us explain.
Yes, FINALLY, we are extremely excited to announce support for nostr.build (blossom.band) on Primal! Decades in the making, billions of people have been waiting, and now it’s available! But it’s not just any integration, it is the next level of decentralized media hosting for Nostr. Let us explain. Primal is an advanced Twitter/X like client for Nostr and is probably the fastest up-and-coming, highly used Nostr app available for iOS, Android and the web. Nostr.build is a very popular media hosting service for Nostr that can be used standalone or integrated into many Nostr apps using nip-96. This is an extremely feature rich, tested and proven integration we recommend for most applications, but it’s never been available on Primal.
And then, Blossom was born, thank you Hzrd149! Blossom is a Nostr media hosting protocol that makes it extremely easy for Nostr clients to integrate a media host, and for users of Blossom media hosts (even an in-house build) to host on any Nostr client. Revolutionary, right! Use whatever host you want on any client you want, the flexible beauty of Nostr. But there is an additional feature to Blossom that is key, mirroring.
One of the biggest complaints to media hosting on Nostr is, if a media hosting service goes down, so does all of the media hosted on that service. No bueno, and defeats the whole decentralized idea behind Nostr.. This has always been a hard problem to solve until Blossom mirroring came along. Mirroring allows a single media upload to be hosted on multiple servers using its hash, or unique media identifier. This way, if a media host goes down, the media is still available and accessible on the other host.
So, we are not only announcing support of nostr.build’s blossom.band on the Primal app, we are also announcing the first known fully integrated implementation of mirroring with multiple media hosts on Nostr. Try it out for yourself! Go to the settings of your Primal web, iOS or Android app, choose ‘Media Servers’, enable ‘Media Mirrors’, and add https://blossom.band and https://blossom.primal.net as your Media server and Mirror, done!
Video here!
-
 @ 2ce0697b:1ee3d3fc
2025-04-29 18:54:19
@ 2ce0697b:1ee3d3fc
2025-04-29 18:54:19Excerpt
Special Jurisdictions, Free Cities and Bitcoin Citadels are the sly roundabout way that is removing the market of living together from the hands of the government, without violence and in a way that they can´t stop it. With Bitcoin as the backbone of a new societal order, we are beginning to disrupt the old paradigm.
“If you have built castles in the air, your work need not be lost; that is where they should be. Now put the foundations under them.” ― Henry David Thoreau, Walden
The problem: lack of freedom in the physical realm
Freedom is essential to human life. Being free is what matters. That´s our target, always. No matter the time or space. We pursue freedom because we know its the right thing to do. Freedom is the right to question and change the stablished way of doing things.
Where can we find some freedom? Certainly in the cyberspace. The cyberspace is a free space. Humanity has been blessed by the magic of cryptography, a technology that gave us all the necessary tools to operate in that environment without intervention of undesired third parties.
In cyberspace cryptography performs the function of an impenetrable cyberwall. So, whatever we build in cyberspace can be perfectly protected. Thank to this cybernetic walls we can be sure that the gardens we build and nurture will be protected and cannot be trampled. When we build our digital gardens we have the keys to open the doors to let in whoever we want and most important to leave out whoever we don´t want. In the digital world we can already perfectly interact with one and another in a peer to peer way, without intervention of undesired third parties.
In cyberspace we have Bitcoin for freedom of money and Nostr, torrent and Tor for freedom of information and speech. These open-source protocols are designed to fully realize and expand the promise of freedom, and they certainly deliver what they promise.

So, thanks to the magic of asymmetric cryptography, we´ve already achieved sufficiently descentralization and the possibility of any level of desired digital privacy. Cryptoanarchists and cypherpunks have set their conquering flag in cyberspace and there´s no force on Earth than can remove it. The digital world cannot escape the rules of cryptography. This is great but it only works in the digital realm, meanwhile in the physical realm we are overrun by centralized attackers due to the impossibility of the creation of impenetrable walls such as the ones we have online.
Humans have the upper hand in creating impenetrable walled gardens in cyberspace, but in the physical space authoritarians have the upper hand in bullying physical persons.
The physical world is also naturally free. According to natural law each person is free to do whatever he wants as long as it doesn´t hurt other people. However due to unnatural -artificial and inhuman- centralization of power, the natural freedom of the physical world has been completely undermined. Mostly by Governments, the entities that centralize violence and law.
Bitcoin as a bridge between both realms

Let´s take a look at one connection between both realms, the physical and the digital world. Bitcoin layer one is made essentially of software plus hardware. It consists of any software that produces the same output as the reference implementation - Bitcoin core- and the hardware needed to run that software. Layer two, three or any other layer above, is made essentially of other software and other hardware that interacts with layer one in some way. All these layers, one, two and subsequent, are completely protected by cryptography and a set of game theories that have been successfully tested. Each new block added to the timechain is a testimony of the unstoppable force of freedom and meritocracy.
Before layer one we have Bitcoin layer zero, which is essentially the sum of all actions and inactions done by bitcoiners regarding to or because of bitcoin. In other words, layer zero is composed by flesh and bone people interacting in some way with layer one of the bitcoin network.
Hence, an attack on a bitcoiner - on his way of life- is an attack on bitcoin, the network itself. First because it is an attack on a layer zero node, the physical person, the bitcoiner under duress or coercion. And second because is also an attack on the store-of-value-aspect of bitcoin. Nowaday, the most common attack against bitcoiners is the entirety of compliance regulations. This is the sum of all coercive regulations,such as laws, threats of more laws, imprisonment, threats of more imprisonment, taxation, threats of more taxation, requirements to prove the origin of funds, coercive removal of privacy such as the travel rule, unnecessary bureaucracy such as the need to obtain a money transmitting license and many others rules, in a never stopping inflationary coercive legislation.

If a physical attack is preventing any bitcoiner to exchange the value he created for bitcoin due to any kind of artificial obstacles -such as any kind of compliance- that specific attack is successful in the sense that even though the whole network keeps operating, the attack itself diminishes the value of all the bitcoins.
So, even if layer-zero cannot be taken down, every interference on this layer is an attack on the bitcoin network. Attacks on layer one, two or any other layer that exists in the cyberspace can interfere with the network but they may hardly subtract any value from it. For example we have already been through plenty of times where hashing power was diminished due to government intervention and the bitcoin network remain completely unaffected.
On the other hand successful attacks on layer zero subtract potential, but real and demonstrable value. This value is equal to the amount of value the frustrated user would have added to the network if he would have been able to use it freely, that means if he would have sold his product without the cost of compliance. I´ll demonstrate this in the next chapter.
The cost of compliance
Alice is a merchant specialized in a specific area and topic. She studied the market, her business, her suppliers, consumers, the logistics involved, marketing, design, and everything necessary to become a successful entrepreneur. After investing a considerable amount of resources, she developed a perfect product. Or at least she considers it perfect, that is, the best in its class. While developing everything necessary to create her product, she met Bob, who became her main lead and stereotype of a buyer persona. She knows what Bob wants and she wants to sell it to him. According to Alice's calculations, for her business to be viable, she must sell the product at ten satoshis per unit, and fortunately, Bob is willing to pay that price for it. Alice's product is finished, ready to hit the market, but just before sending it to production, Alice decides to take a pause to analyze her reality. Before taking the public action of making her product available in the open market, Alice analyzes her material, political, and legal reality. In doing so, she realizes that she lives under the jurisdiction of a State. She learns that the Government prescribes through its regulations how she must behave. She analyzes that in order to sell her product legally, in compliance, she must make a series of modifications to it. The product before hitting the shelves must first be modified both in the way it is presented to the market and also regarding certain technical characteristics that it possesses. She must also modify the way it produces her product by changing the contractual relationship with its suppliers, distribution channels, and all other types of logistics involved. She must make all these changes even if they bring about significant and insurmountable inefficiencies.
Likewise, Alice also sees that she not only has to modify the product but also has to meet tax obligations. In addition to paying an accountant since the tax obligations by some irrational reason are not calculated by the creditor. Additionally, she must hire other professionals to assist her in studying the current regulations and how they should be applied in all stages of production, distribution, and sale of her product.
Alice, being a rational person, wishes to avoid having to make these modifications since they increase her costs while also decreasing the quality of her product. But when studying compliance, that is, the entirety of applicable regulations, she also examines the consequences of not being in compliance. Alice realizes that if she does not comply with the regulations, she risks having all her assets legally confiscated, going to prison, being killed while they try to capture her to imprison her, and, if she goes to prison, being tortured in jail by other inmates or by State officials in charge of holding her in that place. So, since Alice does not want to suffer these negative consequences, she decides to modify the product and be in compliance.
So, Alice makes the necessary changes and puts her new version of the product on the market. Then she has the following dialogue with Bob, her lead, the interested party in acquiring the product.
Bob: - Hey Alice, nice meeting you here in this market. I came to buy the product you were developing and told me about. However, this product I´m seeing now is not what you promised me. This is clearly inferior.
Alice: - Yeah, I know. I'm sorry Bob, but I prefer to sell this inferior product rather than risk having all my assets confiscated, going to prison, being killed while they try to capture me, and if they don´t kill but managed to put me in jail I could be tortured there.
Bob: - Ok, no problem. Thats quite understandable. I don´t believe anyone would prefer those kind of experiences. But given the quality of the product, I no longer intend to pay you ten satoshis; I only offer you eight. Shall we close the deal?
Alice: - I'm sorry Bob, but I can't sell it to you for eight sats. Due to government intervention and its requirements, now I can't even sell it for less than thirteen satoshis.
Bob: - Ok. Considering this I prefer not to purchase it. I will keep looking for alternatives. Bye

Some time later, Charlie arrives at the market, who is also interested in the product and, despite it not being like the original version, decides to purchase it by paying the thirteen satoshis demanded by the seller Alice.
Meanwhile, in the same universe, we have Daniel, the last character in this example. Daniel is a merchant competing with Alice. Daniel has a product that is very similar, practically identical to the one originally designed by Alice. Like Alice, Daniel initially also wants to sell it for ten satoshis. Just like Alice, before heading to the market, Daniel analyzes the reality in which he lives. And it turns out that he also lives under the jurisdiction of a State. Daniel too then analyzes the entirety of the applicable regulations and also comes to the conclusion that to comply with them, he would also need to modify the product and cover all the additional expenses artificially generated to be in compliance.
However, Daniel's ethics are different from Alice's. Daniel understands that his product is indeed perfect (the best in its class) and that therefore modifying it would go against its essence. Daniel understands that changing the product would be a betrayal of his creation and therefore a betrayal of his own self and the essence of his being. Daniel conducts an ethical analysis of his actions and the moral implications of putting the product on the market. Daniel sees that the product not only does not harm anyone but is also made to be freely acquired by adults who give their consent for its purchase and subsequent use. Daniel also understands that paying taxes only serves to promote the slavery system driven by fiat and that whenever he can avoid collaborating with the immoral fiat system, it is his ethical obligation to do so. Likewise, Daniel highlights the hypocrisy and inefficiencies of anti-money laundering regulations, as well as the futility of requiring licenses for naturally free acts that do not harm others. For all these reasons, Daniel decides to sell the product in its current state irregardles of compliance regulations.
However, before going to market, Daniel also studies the possible consequences of neglecting compliance. By doing so, Daniel sees that if he does not comply with the regulations, he risks having all his assets legally confiscated, going to prison, being killed while they attempt to capture him to imprison him, and, in the event of going to prison, being tortured in jail by other inmates or by State officials responsible for holding him in that place. So, since Daniel is a rational person who does not want to suffer these negative consequences but also does not want to betray his product and himself, he decides to take the risk of not being in compliance. After making this decision, Daniel puts the product on the market and there he meets Bob. In doing so, they converse in the following terms:
Bob: - Hey Daniel, this product is exactly what I was looking for. A product like the one promised by Alice but never delivered. I love it! I offer you ten satoshis for it.
Daniel: - Thank you for your feedback Bob and for the offer! However I am currently selling it for eleven satoshis. Ten satoshis seems like a good price to me, and it was indeed my original intention to sell it for that amount because at that price I achieve competitiveness and a sustainable business model.
Bob: - So why are you asking me for eleven satoshis? Interrupts Bob
Daniel: - Because that price is calculated before assessing compliance and the risks associated with non-compliance. By not complying with the regulation, I managed to maintain the quality of the product and avoided a large amount of unnecessary expenses, but there is no way to avoid the risk of facing penalties for non-compliance. To bring this product to market, I had to incur several expenses in order to minimize the risk of non-compliance as much as possible. While I am taking all reasonable actions to prevent all of my assets from being legally confiscated, from going to prison, from being killed while they try to capture me, and in case of going to prison, from being tortured, the reality is that I still run the risk of all that, or part of all that, happening to me, my family, or any of my company's employees. The remaining risk balance is transferred to the price along with the costs of mitigating those risks. The total of those costs and the remaining risk I estimate them at one satoshi per unit of product. Therefore, I can't sell you the product for ten satoshis, but I can sell it to you for eleven.
To which Bob, lacking a better option in the market, ends up buying the product for eleven satoshis.
In summary: two products were made by two different merchants whose business model allowed them, in both cases, to put the product on the market at a rate of ten satoshis per unit. However, in one case, a lower quality product was sold for thirteen satoshis, and in the other case, a higher quality product was sold for eleven satoshis. That is to say, in the first case there was an overprice or inefficiency objectively measured at three satoshis, while in the second case there was an overprice or inefficiency of one satoshi. So, we are facing a total loss of value equivalent to four satoshis. The value represented by these four satoshis was absorbed by the inefficiency programmed and ruled by the State. The example shows us that whether one chooses the compliance route, as Alice did, or the free market route, as Daniel did, in both cases the existence of regulations generates an additional cost to the market. In this example the state attack on layer zero was successful and extracted from the Bitcoin network a value of four satoshis.
Bitcoin is money
Bitcoin is many things but essentially is money. And money sole purpose is to store value in order to facilitate future exchanges of products and services with other people. Without the products and services to be exchanged for the money, money itself would be useless and worthless. We only use money because we may require favors, benefits, services, products from other people in the future. And we don´t know which services and products we´ll need nor exactly when we are goint to need them.

The total value of bitcoin equals to infinity divided twenty one millions. This is because the total worth of the network mirrors the total worth of accumulated capital by the entirety of mankind throughout its entire history. That is clearly a lot of value. But if the if the dividend equals zero then the divisor is also zero and if the dividend growth is obstructed through artificial means -such as compliance- then the divisor growth is also obstructed.
Bitcoin layer zero, the bitcoiners and the services and products we create, are what give value to the twenty one million units of bitcoin.
Freedom is without a doubt the best context for value creation. So, the more and better games we can create that allow humankind to find a way to exercise freedom, then the most value we can add to all the layers of the network.
This is why the most important layer of the whole bitcoin phenomenon is layer zero, the bitcoiners. Hence the problem to be solved is not how to prevent bitcoin - layer one upwards- from successful attacks. The problem to solve is how to prevent attacks on layer zero. Or in other words, the problem to be solved is how to get bitcoiners in the physical world to practice the same level of freedom that bitcoin achieves in the cyberspace.
Summary of the first part of this article: freedom in cyberspace has already been conquered and each further development in the digital realm contributes to further developments but only in the same realm. Meanwhile in the physical space, the layer zero of bitcoin is under constant attacks that successfully extract value from it.
Exercising freedom in a sly roundabout way

In 1984 the Austrian economist Friedrich Hayek predicted that we couldn´t take money with violence out of the hands of government. He stated that we needed to do it in a sly roundabout way. Twenty five years later Satoshi Nakamoto discovered the sly roundabout way actually introducing something that the government couldn´t stop. Thus fulfilling Hayek´s prophecy.
Bitcoin is a sly roundabout way that removed money without violence from the hands of the government in a way that they can´t stop it.
Cryptography in general and protocols such as Tor and Tails are a sly roundabout way that removed confidential information from the hands of the government without violence in a way that they can´t stop it.
Nostr is a sly roundabout way that removed social media and public information from the hands of the government without violence in a way that they can´t stop it.
Special Jurisdictions, Free Cities and Bitcoin Citadels are the sly roundabout way that is removing the market of living together from the hands of the government without violence in a way that they can´t stop it.

So, what are Special Jurisdictions, Free Cities and Bitcoin Citadels? To understand what they are we can take a look at the current mainstream market of living together, at how the physical space is organized. Essentially the entire planet Earth and its surroundings are run by a conglomerate of Governments. They create all the rules, regarding every aspect of life, of all the individuals, and enforce every rule through coercive means.
In the mainstream market of living together individuals have several alternatives to pick from. We can choose to live in a natural city or a pre design city, in a public neighborhood or private neighborhood or even in an intentional community with common interest amongst the users. But irregardless of the choice, every product offered in the mainstream market has the sames rules which are established by the host state to the entirety of organizations in his territory. In the mainstream market, even the most different products abide by the same high level rules such as criminal law, civil law, taxation laws, customs, enviromental laws, money laundering regulations and many others. To abide to the sum of all the laws and regulations is to be in compliance.
The centralization of regulations makes extremely difficult to experiment in market of living together. The less experimentation is allowed, the more human progress is hindered.
So what is the sly roundabout that fixes this? What are Special Jurisdictions, Free Cities and Bitcoin Citadels? I´m using the term Special Jurisdictions as an umbrella term that includes the entire spectrum of iterations of products that aim to modify the mainstream rules of the market of living together.
This term includes all the different models such as Charter Cities, Free Cities, Special Economic Zones, microstates, micropolis, start up societies, government as a service, self governing jurisdictions, autonomous intentional communities, network states and Bitcoin Citadels. The array of possible iterations is huge and permanently expanding. What they all have in common is that each of these experiments aims to create a functional game theory that replaces the lack of unbreakable walls in the physical space.
Let´s take a look of a couple of examples. Special Economic Zones are bounded areas of countries that have their own rules and regulations. Worldwide, there are more than five thousands special economic zones located in more than hundred countries.
One of them is the special economic zone of Shenzhen in China. The Chinese government allowed Shenzhen the freedom to experiment with certain practices that were prohibited in the rest of the country at the time. This included allowing foreign companies to make direct investments in China, allowing people to buy and sell land, allowing Chinese people to set up their own private businesses and relaxation of the system that limited internal migration within China for Chinese citizens. It served as a place where China could experiment with market reforms. The experiment was such a huge economic success that it was replicated in many other areas of the country.
Another place that has made extensive use of special economic zones is Dubai. The monarchic Government has more than 30 SEZs. In this case one of the many obstacles removed by the host state its the monopoly of the legal system. Dubai Government allowed the special economic zone to have its own independent legal system thus conceding a modification of the mainstream rules in that area.
This kind of projects, such as Dubai or Shenzhen, are a top-to-down product. Fully created by the Governments thus compliant with their own regulations.

On the other side of the spectrum we have Citadels and several other archetypes of not so compliant projects .
For example the Free Commune of Penadexo it´s a grassroots project building a freedom-oriented community in one of Spain’s abandoned villages.
 It´s model is based on building a peer to peer society avoiding government intervention as much as possible.
They stablished themselves in an abandoned historic village and the started to track down the owners to purchase as much property as possible. Meanwhile, they are living there and expanding their users base while also reconstructing buildings.
It´s model is based on building a peer to peer society avoiding government intervention as much as possible.
They stablished themselves in an abandoned historic village and the started to track down the owners to purchase as much property as possible. Meanwhile, they are living there and expanding their users base while also reconstructing buildings. This is an example of a completely different way of dealing with the Government. While Special Economic Zones are fully compliant and created top to down, this model on the other hand is bottom-up and aims to add value to the users relying in factual freedom which is exercised by stablishing the commune away from heavily populated centers where Government grip is tighter. Under this model the interaction with the Government is kept as low as possible. Their strategy relies in ignoring the Government as much as possible and being a good neighbor. With this simple and effective tactic some Citadels enjoy the benefits of liberty in their lifetime without needing to spend huge resources in governmental lobby.
There are countless models or archetypes of Bitcoin Citadels trying to solve the obstacles in different ways, trying to restart the system. And one of the challenges of the Bitcoin Citadels is how to connect the different projects to boost and help each other.
This is where The Meshtadel comes into play. The Meshtadel is a system where decentralized tactics are used to help and defend citadels connected in a global network. With real life connections with fellow bitcoiners. Its an organization equivalent to the hanseatic league built under a starfish model. If you cut off a spider’s head, it dies, but if you cut off a starfish’s arm, it can regenerate and even grow into a new starfish.
The Meshtadel its a network of peer relationships, with ambiguous leadership roles, trust among participants, a shared ideology and vision based on the Bitcoin ethos, and an open system where new nodes - bitcoin citadel builders - can participate.
The long term goal of the Bitcoin Meshtadel is to help Bitcoin Citadels to gain the support of a critical mass of the total population. If enough people see that Bitcoin is as peaceful as it gets, in the long run, some nations could become friendly and supportive enough to legally tolerate the Bitcoin Citadel inside its territory in the form of a Bitcoin safe haven. In the Meshtadel we are fighting from the moral high ground using memes, Nostr notes and zapping our way into freedom creating an online and offline circular economy.
TO CONCLUDE:
Special Jurisdictions, Free Cities and Bitcoin Citadels are the sly roundabout way that is removing the market of living together from the hands of the government, without violence and in a way that they can´t stop it.
Nation states, abusing the myth of authority, have halted development on the market of living together for so long that a blooming freer market is eating its lunch. The sovereign individual thesis is live and continuously expanding. The network state is forming and intentional communities are flourishing all around the world reshaping globally the relationship between individuals and the governments.
With global internet connections, uncensorable means of communication and Bitcoin as the backbone of a new societal order, we are beginning to disrupt the old paradigm.
The fashion of the present world is passing away, let’s help it to move forward along by building Special Jurisdictions, Free Cities and Bitcoin Citadels.
--- --- --- --- --- --- --- --- ------
byCamiloat 875.341 timechain.
If you find this content helpful, zap it to support more content of the sort and to boost the V4V model.
-
 @ 86d4591f:a987c633
2025-04-30 07:51:50
@ 86d4591f:a987c633
2025-04-30 07:51:50Once upon a time, power wore a crown. Then it wore a top hat. Today, it wears a hoodie and speaks in sanitized mission statements about connection, safety, and user experience. But make no mistake: this is empire — softened, digitized, gamified, but empire all the same.
The old robber barons built railroads and refineries. They captured the flow of goods and oil. The new ones build feeds and filters. They’ve captured the flow of attention, of meaning, of reality itself.
We used to trade in commodities; now we trade in perception. The platform is the factory, your data the raw material, your behavior the product. And like all robber barons, these new lords of code and cloud mask extraction in the language of progress.
They promise frictionless connection while selling surveillance. They promise community while cultivating dependency. They promise democratization while algorithmically anointing kings and silencing dissidents. A swipe, a like, a follow — every gesture is monetized. Every word is moderated. Every post is subject to invisible whims dressed up as “community standards.”
And we? We scroll through curated realities in gilded cages. We call it the feed, but what is it feeding? We’re not the customers — we’re the cattle. The economy has shifted from production to prediction, from ownership to access, from sovereignty to servitude.
The invisible hand now wears visible chains.
But rebellion brews — not as a riot, but as a protocol. Nostr: No gatekeepers. No kill switches. No boardroom behind the curtain. Just a blunt, defiant tool — a new printing press for the digital age.
Nostr isn’t slick. It doesn’t care about onboarding funnels or quarterly growth. It cares about freedom. It is infrastructure for speech that doesn’t ask permission. A raw wire of intent between human beings. An insurgent standard in a world of walled gardens.
This is not just about apps. This is about autonomy. About reclaiming the digital commons. About refusing to let five companies in Silicon Valley draw the borders of acceptable thought.
So plant your flag. Publish what they won’t. Build what they fear. This is not nostalgia for the early web — it is the refusal to let the next web become a prison wrapped in personalization.
The New Robber Barons control the rails of perception.
But we are building tunnels.
Protocol over platform.
Signal over spectacle.
Freedom over frictionless servitude.
Speak freely. Build fiercely. The territory is ours to reclaim.
-
 @ 3c389c8f:7a2eff7f
2025-04-29 18:38:46
@ 3c389c8f:7a2eff7f
2025-04-29 18:38:46Let go of the algorithms and truly discover what it means to explore. Social media used to mean something. Once upon a time, it was a way to stay connected to friends, family, and colleagues over things we enjoy. We could share, laugh, and learn. Over time, it has devolved into cheap entertainment at the cost of our privacy. Our relationships and interests have been shoved into a corner in order to make room for "suggested posts" and "for you" content designed to evaluate our attention for advertising purposes. We've lost what it means to truly connect, and we've lost what it means to explore our curiosities.
Enter Nostr. A protocol designed to resist authoritative censorship, just happens to fix a whole lot of other problems, too. By removing the central authority, Nostr offers its users complete control of what we feed our minds. How do we break our algorithm dependency to find better content and better relationships again? We explore and discover:
The Chronological Life.
The existence of time may be debatable but our dependence on our perception of it is not. We live our lives chronologically. Why do our online lives need to be any different? There is no real reason, other than we've just gotten used to being engulfed by whatever the black box wants us to see. When we remove the algorithms, we find that online information flows just as it would in our daily lives. Important events get talked about by many people, over a long period of time. Things of less relevance fade. We see the rhythm of life reflected in our feed. This is an organic human experience transferred to the digital world. We depend on the people we know and the sources we trust to keep us informed about what really matters. We have fun, we move on. Nearly every Nostr social client brings this experience front and center through the traditional follow feed. Many use replies as a way to show you what is worth talking about for more than a hot minute. Its what old social media gave us, then took away. Nostr gives it back. It's not the only way to enjoy Nostr, though, so let's continue.
"The Human Animal Differs From the Lesser Primates in His Passion for Lists"
Who doesn't love lists? (besides maybe to-do lists.) List functionality on Nostr is a powerful way to curate your feeds. You can make lists of artists, vendors, friends, or whatever you want. They can be public or private. You can subscribe to other people's public lists too. Make one to share with your friends. Many clients have list support and management. Amethyst, Nostur, Voyage, and Nostrudel are a few that come to mind. Nostr.band and Listr.lol offer in depth list management. Some clients even support lists for specific notes so that you can curate a feed by topic or aesthetic to share with your friends.
Being John Malcovich.
Everyone has a different view of Nostr. Do you want to see what someone else is seeing? Sign in with any npub to get a different perspective. You might find profiles and content that you didn't know existed before. Some clients integrate variations of this feature right into their apps, so you don't have to log out of your account in order to step through that tiny door.
DV-what? DVM.
Data Vending Machines. These fancy little things are AIs tasked with a simple job: to find content for you. Most of these feeds are free, though some more personalized ones require a small fee. Many DVM services are stand-alone apps, like Vendata and Noogle . These clever Nostr clients will let you do a lot more than just create feeds to browse notes. Explore if you wish. A few social clients have DVMs integrated, too, so if you see "discovery" or similar term on a tab, be sure to check it out.
Relays, Man. Relays.
It's right there in the name. Nostr- notes and other stuff transmitted by RELAY. Specialized relays exist for subjects, news, communities, personal spaces, content creators, cats... there's even a relay where everyone just says "Good Morning" to each other. Find a client that lets you browse a relay's contents, and enjoy the purest form of content discovery on Nostr. Unearthing these relays is getting better and better every day. Right now there are relay browsing capabilities in quite a few clients, like Coracle, Relay Tools, Jumble and Nostur.
The Algo Relay.
Maybe you've been busy and missed a lot. Maybe you are a sane person who rarely uses social media. Hook up with a personalized algorithm relay to catch you up on all the things you've missed. This is skirting the sharp edges of Nostr relay development, so keep in mind that not many implementations yet exist. Algo relay currently aims to bring the feel-good vibe of your chronological feed to an algorithmic feed, freeing up your time but letting you stay up with what 's going on in your social circles.
Trendy Trends.
A few clients, relays, and DVM's have developed various Trending feeds. Catch up on what's popular across a wider view of the Nostr ecosystem. If trends are your thing, be sure to check them out.
Now that you're equipped with the tools to explore Nostr, its time to go discover some great content and find your people. Feed your curiosity.
-
 @ fd06f542:8d6d54cd
2025-04-30 03:49:30
@ fd06f542:8d6d54cd
2025-04-30 03:49:30今天介绍一个 long-form 项目,源代码在:
https://github.com/dhalsim/nostr-static
从项目的介绍看也是为了展示kind 30023 long-form的。
Demo
https://blog.nostrize.me
界面还可以:
 {.user-img}
{.user-img}- 支持多个tags
- 支持评论
下面看他自己的介绍:
nostr-static是一个开源项目,其主要目的是将 Nostr 网络上的长文内容转化为静态博客。下面从多个方面对该项目进行分析:1. 项目概述
nostr-static是一个静态网站生成器(SSG)工具,它可以从 Nostr 网络中获取长文内容,并生成可在任何地方托管的 HTML 页面。这使得用户能够轻松地创建和维护由 Nostr 内容驱动的博客,同时结合了去中心化内容和传统网站托管的优点。2. 功能特性
- 内容转换:能够将 Nostr 上的长文内容转化为美观的静态博客页面,博客加载速度快。
- 去中心化与传统结合:文章存储在 Nostr 网络上,保证了内容的去中心化,同时为读者提供了熟悉的博客界面。
- 易于维护:通过简单的配置和自动更新功能,降低了博客的维护成本。
- 灵活的托管方式:支持多种静态网站托管服务,如 Netlify、Vercel、Cloudflare Pages、Amazon S3 以及传统的 Web 托管服务。
- 社交互动:可以利用 Nostr 进行评论等社交互动。
3. 技术实现
- 前端:从代码片段可以看出,项目使用了 HTML 和 CSS 来构建页面布局和样式,同时支持明暗两种主题模式。页面包含文章卡片、标签、作者信息等常见博客元素。
- 后端:项目使用 Go 语言编写,通过
go build -o nostr-static ./src && ./nostr-static命令进行构建和运行。 - 数据获取:从 Nostr 网络中获取文章内容,需要提供 Nostr naddr 信息。
4. 使用步骤
根据
README.md文件,使用该项目的步骤如下: 1. Fork 项目仓库。 2. 将项目克隆到本地或使用 GitHub Codespaces。 3. 修改config.yaml文件进行配置。 4. 在articles列表中添加要展示的 Nostr naddr。 5. 将logo.png文件放入项目文件夹(如果文件名不同,需要在config.yaml中更新)。 6. 构建并运行项目。 7. 提交并推送更改。5. 项目优势
- 创新性:结合了 Nostr 的去中心化特性和传统博客的易用性,为博主提供了一种新的博客创建方式。
- 简单易用:通过简单的配置和命令即可完成博客的创建和部署,降低了技术门槛。
- 社区支持:开源项目可以吸引更多开发者参与贡献,不断完善功能和修复问题。
nostr-static是一个有创新性和潜力的项目,为 Nostr 用户提供了一种将长文内容转化为传统博客的有效方式。随着项目的不断发展和完善,有望在博客领域获得更多的关注和应用。 -
 @ 3c389c8f:7a2eff7f
2025-04-29 18:13:50
@ 3c389c8f:7a2eff7f
2025-04-29 18:13:50TL;DR visit this post for a list of signers
Your nsec/private key is your key to controlling all that you do on Nostr. Every action you take is signed by this private key, validating that was you that generated that event, whether it be a note, a like, a list, or whatever else. Like a broken record, I have to state that it is irreplaceable. YOU own your identity and no one else. It is your responsibility to keep your nsec safe, but of course, you also want to be able to use all the different apps and clients available. To aid you in this process, a few different tools have been developed. Let's take a look at some that are more common and easy-to-use, where to use them, and for what.
The Browser Extension
This is probably the simplest and most straight forward form of private key manager available. There are many options to choose from, each compatible with various, commonly used browsers, including mobile browsers. Many provide the option to manage multiple keys for different profiles. Some are simply a signer while others may include other features. The concept is very simple. The extension holds your key and exposes it only only enough to sign an event. These extensions can be set to different levels of manual approval that you can control based on the level of convenience you seek. The ease and convenience does trade off a bit of security, as your private key will be exposed momentarily each time you create an event. It is up to you to choose whether this is appropriate for your use. For casual browsing and social media use, it is a fairly good and easy to use option. Nearly all Nostr apps and clients support signing with this method.
The Remote Signer
Often referred as a "bunker", Nostr remote signers hold your private key completely offline and communicating with clients. Clients send events to the signer to be signed, which then sends back the signed event for publishing. This bunker can be hosted on your own hardware or managed by a truested 3rd party. As long as the signer is online, it can communicate as needed. The signer generates a "bunker string" that is used to communicate. These may seem cumbersome to set up, as each client that you intend to use will need its own permissions. Once all of the pieces and permissions are in place, most of this activity will happen in the background. Bunkers allow for a lot of flexibility. The "bunker string" for a single app can be shared with other users who you may want to be able to make posts on your behalf. Multiple people can manage a social media profile, while the main owner of that identity maintains control of the nsec. These bunker strings can be revoked and replaced at any time. This signing method is growing in popularity and many clients already offer support for it.
The Native Android Signer
Currently, Amber is the only native app available to handle Nostr event signing. It is an incredible tool for managing your Nostr key on your mobile device. The signing flow is similar to remote signing, as described above, but it can communicate with both your Android native Nostr apps and web clients accessed through most mobile browsers, eliminating the need for a browser extension. Similar apps are under development for iOS, but I don't use any of those devices, so covering that here will only happen via other's opinions at a later date. Check this list for current options.
NcryptSec
NcryptSec signing works by encrypting your nsec on a local device, unlocked by a password that you choose. Support for this method is very limited, as the encrypted private key stays on your device. If you intend to use Nostr through one device and few apps, this can be a very secure option, as long as you can remember your password, as it cannot be changed.
NFC and Hardware Signers
Some devices have been developed to store your nsec completely offline on a device or NFC chip, and some clients have added support for scanning/connecting to sign. I haven't personally tried any of these options, nor do I intend to promote the sale of any particular products. If you are interested in these techniques and devices, the information is not hard to find. The price of a devices varies, depending on your feature needs.
There are also DIY options that utilize existing hardware, if you are into that sort of thing.
Higher Security and Recoverability Options
Creating a scheme that allows for recovery of a lost key while maintaining the integrity of a unique identity is no easy task. The key must be fractured into shards, encrypted, and distributed across multiple servers in various locations, while you maintain a portion or portions of your own. These servers are run by trusted 3rd parties who will then sign events "with" you. Some include a scheme of running your own always online hardware to act as host for these shards. I fall short on the technical understanding of certain aspects of these processes, so I will spare you of my attempt to explain. As far as I know, there are a couple of methods underway that are worth paying attention to:
Frostr nostr:nevent1qvzqqqqqqypzqs3fcg0szqdtcway2ge7zahfwhafuecmkx9xwg4a7aexhgj5ghleqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcqyrh3r7uhytc4dywjggxz24277xgqtvcadvnjfks6fram7gjpev9nuentfht
Promenade nostr:nevent1qvzqqqqqqypzqwlsccluhy6xxsr6l9a9uhhxf75g85g8a709tprjcn4e42h053vaqydhwumn8ghj7un9d3shjtnhv4ehgetjde38gcewvdhk6tcprdmhxue69uhhyetvv9ujuam9wd6x2unwvf6xxtnrdakj7qpqqqq0dlpwxhw5l97yrcts2klhr9zqqpcmdfpaxm8r7hygykp630cq23ggph
For a List of signers, please visit this post.
-
 @ f11e91c5:59a0b04a
2025-04-30 07:52:21
@ f11e91c5:59a0b04a
2025-04-30 07:52:21!!!2022-07-07に書かれた記事です。
暗号通貨とかでお弁当売ってます 11:30〜14:00ぐらいでやってます
◆住所 木曜日・東京都渋谷区宇田川町41 (アベマタワーの下らへん)
◆お値段
Monacoin 3.9mona
Bitzeny 390zny
Bitcoin 3900sats (#lightningNetwork)
Ethereum 0.0039Ether(#zkSync)
39=thank you. (円を基準にしてません)
最近は週に一回になりました。 他の日はキッチンカーの現場を探したり色々してます。 東京都内で平日ランチ出店出来そうな場所があればぜひご連絡を!
 写真はNFCタグです。
スマホにウォレットがあればタッチして3900satsで決済出来ます。
正直こんな怪しい手書きのNFCタグなんて絶対にビットコイナーは触りたくも無いだろうなと思いますが、これでも良いんだぜというメッセージです。
写真はNFCタグです。
スマホにウォレットがあればタッチして3900satsで決済出来ます。
正直こんな怪しい手書きのNFCタグなんて絶対にビットコイナーは触りたくも無いだろうなと思いますが、これでも良いんだぜというメッセージです。今までbtcpayのposでしたが速度を追求してこれに変更しました。 たまに上手くいかないですがそしたら渋々POS出すので温かい目でよろしくお願いします。
ノードを建てたり決済したりで1年経ちました。 最近も少しずつノードを建てる方が増えてるみたいで本当凄いですねUmbrel 大体の人がルーティングに果敢に挑むのを見つつ 奥さんに土下座しながら費用を捻出する弱小の私は決済の利便性を全開で振り切るしか無いので応援よろしくお願いします。
あえて あえて言うのであれば、ルーティングも楽しいですけど やはり本当の意味での即時決済や相手を選んでチャネルを繋げる楽しさもあるよとお伝えしたいっ!! 決済を受け入れないと分からない所ですが 承認がいらない時点で画期的です。
QRでもタッチでも金額指定でも入力でも もうやりようには出来てしまうし進化が恐ろしく早いので1番利用の多いpaypayの手数料(事業者側のね)を考えたらビットコイン凄いじゃない!と叫びたくなる。 が、やはり税制面や価格の変動(うちはBTC固定だけども)ウォレットの操作や普及率を考えるとまぁ難しい所もあるんですかね。
それでも継続的に沢山の人が色んな活動をしてるので私も何か出来ることがあれば 今後も奥さんに土下座しながら頑張って行きたいと思います。
(Originally posted 2022-07-07)
I sell bento lunches for cryptocurrency. We’re open roughly 11:30 a.m. – 2:00 p.m. Address Thursdays – 41 Udagawa-chō, Shibuya-ku, Tokyo (around the base of Abema Tower)
Prices Coin Price Note Monacoin 3.9 MONA
Bitzeny 390 ZNY Bitcoin 3,900 sats (Lightning Network)
Ethereum 0.0039 ETH (zkSync) “39” sounds like “thank you” in Japanese. Prices aren’t pegged to yen.These days I’m open only once a week. On other days I’m out scouting new spots for the kitchen-car. If you know weekday-lunch locations inside Tokyo where I could set up, please let me know!
The photo shows an NFC tag. If your phone has a Lightning wallet, just tap and pay 3,900 sats. I admit this hand-written NFC tag looks shady—any self-respecting Bitcoiner probably wouldn’t want to tap it—but the point is: even this works!
I used to run a BTCPay POS, but I switched to this setup for speed. Sometimes the tap payment fails; if that happens I reluctantly pull out the old POS. Thanks for your patience.
It’s been one year since I spun up a node and started accepting Lightning payments. So many people are now running their own nodes—Umbrel really is amazing. While the big players bravely chase routing fees, I’m a tiny operator scraping together funds while begging my wife for forgiveness, so I’m all-in on maximising payment convenience. Your support means a lot!
If I may add: routing is fun, but instant, trust-minimised payments and the thrill of choosing whom to open channels with are just as exciting. You’ll only understand once you start accepting payments yourself—zero-confirmation settlement really is revolutionary.
QR codes, NFC taps, fixed amounts, manual entry… the possibilities keep multiplying, and the pace of innovation is scary fast. When I compare it to the merchant fees on Japan’s most-used service, PayPay, I want to shout: “Bitcoin is incredible!” Sure, taxes, price volatility (my shop is BTC-denominated, though), wallet UX, and adoption hurdles are still pain points.
Even so, lots of people keep building cool stuff, so I’ll keep doing what I can—still on my knees to my wife, but moving forward!
-
 @ 3c389c8f:7a2eff7f
2025-04-29 18:07:00
@ 3c389c8f:7a2eff7f
2025-04-29 18:07:00Extentions:
https://chromewebstore.google.com/detail/flamingo-%E2%80%93-nostr-extensio/alkiaengfedemppafkallgifcmkldohe
https://chromewebstore.google.com/detail/nos2x/kpgefcfmnafjgpblomihpgmejjdanjjp
https://chromewebstore.google.com/detail/aka-profiles/ncmflpbbagcnakkolfpcpogheckolnad
https://keys.band/
https://github.com/haorendashu/nowser
The Remote Signer:
https://nsec.app/
https://github.com/kind-0/nsecbunkerd
Native Android Signer:
https://github.com/greenart7c3/amber
iOS
https://testflight.apple.com/join/8TFMZbMs
https://testflight.apple.com/join/DUzVMDMK
Higher Security Options: To start using Nostr with a secure, recoverable keypair: https://nstart.me/en
For Existing Keys: https://www.frostr.org/
Thank you to https://nostr.net/ for keeping a thorough list of Nostr apps, clients, and tools!
-
 @ 57d1a264:69f1fee1
2025-04-30 07:44:21
@ 57d1a264:69f1fee1
2025-04-30 07:44:21- The Dangers of Ignorance
- A Brief History of Mechanistic Interpretability
- The Utility of Interpretability
- What We Can Do
The progress of the underlying technology is inexorable, driven by forces too powerful to stop, but the way in which it happens—the order in which things are built, the applications we choose, and the details of how it is rolled out to society—are eminently possible to change, and it’s possible to have great positive impact by doing so. We can’t stop the bus, but we can steer it.
—Dario Amodeioriginally posted at https://stacker.news/items/967193
-
 @ 266815e0:6cd408a5
2025-04-29 17:47:57
@ 266815e0:6cd408a5
2025-04-29 17:47:57I'm excited to announce the release of Applesauce v1.0.0! There are a few breaking changes and a lot of improvements and new features across all packages. Each package has been updated to 1.0.0, marking a stable API for developers to build upon.
Applesauce core changes
There was a change in the
applesauce-corepackage in theQueryStore.The
Queryinterface has been converted to a method instead of an object withkeyandrunfields.A bunch of new helper methods and queries were added, checkout the changelog for a full list.
Applesauce Relay
There is a new
applesauce-relaypackage that provides a simple RxJS based api for connecting to relays and publishing events.Documentation: applesauce-relay
Features:
- A simple API for subscribing or publishing to a single relay or a group of relays
- No
connectorclosemethods, connections are managed automatically by rxjs - NIP-11
auth_requiredsupport - Support for NIP-42 authentication
- Prebuilt or custom re-connection back-off
- Keep-alive timeout (default 30s)
- Client-side Negentropy sync support
Example Usage: Single relay
```typescript import { Relay } from "applesauce-relay";
// Connect to a relay const relay = new Relay("wss://relay.example.com");
// Create a REQ and subscribe to it relay .req({ kinds: [1], limit: 10, }) .subscribe((response) => { if (response === "EOSE") { console.log("End of stored events"); } else { console.log("Received event:", response); } }); ```
Example Usage: Relay pool
```typescript import { Relay, RelayPool } from "applesauce-relay";
// Create a pool with a custom relay const pool = new RelayPool();
// Create a REQ and subscribe to it pool .req(["wss://relay.damus.io", "wss://relay.snort.social"], { kinds: [1], limit: 10, }) .subscribe((response) => { if (response === "EOSE") { console.log("End of stored events on all relays"); } else { console.log("Received event:", response); } }); ```
Applesauce actions
Another new package is the
applesauce-actionspackage. This package provides a set of async operations for common Nostr actions.Actions are run against the events in the
EventStoreand use theEventFactoryto create new events to publish.Documentation: applesauce-actions
Example Usage:
```typescript import { ActionHub } from "applesauce-actions";
// An EventStore and EventFactory are required to use the ActionHub import { eventStore } from "./stores.ts"; import { eventFactory } from "./factories.ts";
// Custom publish logic const publish = async (event: NostrEvent) => { console.log("Publishing", event); await app.relayPool.publish(event, app.defaultRelays); };
// The
publishmethod is optional for the asyncrunmethod to work const hub = new ActionHub(eventStore, eventFactory, publish); ```Once an
ActionsHubis created, you can use therunorexecmethods to execute actions:```typescript import { FollowUser, MuteUser } from "applesauce-actions/actions";
// Follow fiatjaf await hub.run( FollowUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d", );
// Or use the
execmethod with a custom publish method await hub .exec( MuteUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d", ) .forEach((event) => { // NOTE: Don't publish this event because we never want to mute fiatjaf // pool.publish(['wss://pyramid.fiatjaf.com/'], event) }); ```There are a log more actions including some for working with NIP-51 lists (private and public), you can find them in the reference
Applesauce loaders
The
applesauce-loaderspackage has been updated to support any relay connection libraries and not justrx-nostr.Before:
```typescript import { ReplaceableLoader } from "applesauce-loaders"; import { createRxNostr } from "rx-nostr";
// Create a new rx-nostr instance const rxNostr = createRxNostr();
// Create a new replaceable loader const replaceableLoader = new ReplaceableLoader(rxNostr); ```
After:
```typescript
import { Observable } from "rxjs"; import { ReplaceableLoader, NostrRequest } from "applesauce-loaders"; import { SimplePool } from "nostr-tools";
// Create a new nostr-tools pool const pool = new SimplePool();
// Create a method that subscribes using nostr-tools and returns an observable function nostrRequest: NostrRequest = (relays, filters, id) => { return new Observable((subscriber) => { const sub = pool.subscribe(relays, filters, { onevent: (event) => { subscriber.next(event); }, onclose: () => subscriber.complete(), oneose: () => subscriber.complete(), });
return () => sub.close();}); };
// Create a new replaceable loader const replaceableLoader = new ReplaceableLoader(nostrRequest); ```
Of course you can still use rx-nostr if you want:
```typescript import { createRxNostr } from "rx-nostr";
// Create a new rx-nostr instance const rxNostr = createRxNostr();
// Create a method that subscribes using rx-nostr and returns an observable function nostrRequest( relays: string[], filters: Filter[], id?: string, ): Observable
{ // Create a new oneshot request so it will complete when EOSE is received const req = createRxOneshotReq({ filters, rxReqId: id }); return rxNostr .use(req, { on: { relays } }) .pipe(map((packet) => packet.event)); } // Create a new replaceable loader const replaceableLoader = new ReplaceableLoader(nostrRequest); ```
There where a few more changes, check out the changelog
Applesauce wallet
Its far from complete, but there is a new
applesauce-walletpackage that provides a actions and queries for working with NIP-60 wallets.Documentation: applesauce-wallet
Example Usage:
```typescript import { CreateWallet, UnlockWallet } from "applesauce-wallet/actions";
// Create a new NIP-60 wallet await hub.run(CreateWallet, ["wss://mint.example.com"], privateKey);
// Unlock wallet and associated tokens/history await hub.run(UnlockWallet, { tokens: true, history: true }); ```
-
 @ fd0bcf8c:521f98c0
2025-04-29 13:38:49
@ fd0bcf8c:521f98c0
2025-04-29 13:38:49The vag' sits on the edge of the highway, broken, hungry. Overhead flies a transcontinental plane filled with highly paid executives. The upper class has taken to the air, the lower class to the roads: there is no longer any bond between them, they are two nations."—The Sovereign Individual
Fire
I was talking to a friend last night. Coffee in hand. Watching flames consume branches. Spring night on his porch.
He believed in America's happy ending. Debt would vanish. Inflation would cool. Manufacturing would return. Good guys win.
I nodded. I wanted to believe.
He leaned forward, toward the flame. I sat back, watching both fire and sky.
His military photos hung inside. Service medals displayed. Patriotism bone-deep.
The pendulum clock on his porch wall swung steadily. Tick. Tock. Measuring moments. Marking epochs.
History tells another story. Not tragic. Just true.
Our time has come. America cut off couldn't compete. Factories sit empty. Supply chains span oceans. Skills lack. Children lag behind. Rebuilding takes decades.
Truth hurts. Truth frees.
Cycles
History moves in waves. Every 500 years, power shifts. Systems fall. Systems rise.
500 BC - Greek coins changed everything. Markets flourished. Athens dominated.
1 AD - Rome ruled commerce. One currency. Endless roads. Bustling ports.
500 AD - Rome faded. Not overnight. Slowly. Trade withered. Cities emptied. Money debased. Roads crumbled. Local strongmen rose. Peasants sought protection. Feudalism emerged.
People still lived. Still worked. Horizons narrowed. Knowledge concentrated. Most barely survived. Rich adapted. Poor suffered.
Self-reliance determined survival. Those growing food endured. Those making essential goods continued. Those dependent on imperial systems suffered most.
1000 AD - Medieval revival began. Venice dominated seas. China printed money. Cathedrals rose. Universities formed.
1500 AD - Europeans sailed everywhere. Spanish silver flowed. Banks financed kingdoms. Companies colonized continents. Power moved west.
The pendulum swung. East to West. West to East. Civilizations rose. Civilizations fell.
2000 AD - Pattern repeats. America strains. Digital networks expand. China rises. Debt swells. Old systems break.
We stand at the hinge.
Warnings
Signs everywhere. Dollar weakens globally. BRICS builds alternatives. Yuan buys oil. Factories rust. Debt exceeds GDP. Interest consumes budgets.
Bridges crumble. Education falters. Politicians chase votes. We consume. We borrow.
Rome fell gradually. Citizens barely noticed. Taxes increased. Currency devalued. Military weakened. Services decayed. Life hardened by degrees.
East Rome adapted. Survived centuries. West fragmented. Trade shrank. Some thrived. Others suffered. Life changed permanently.
Those who could feed themselves survived best. Those who needed the system suffered worst.
Pendulum
My friend poured another coffee. The burn pile popped loudly. Sparks flew upward like dying stars.
His face changed as facts accumulated. Military man. Trained to assess threats. Detect weaknesses.
He stared at the fire. National glory reduced to embers. Something shifted in his expression. Recognition.
His fingers tightened around his mug. Knuckles white. Eyes fixed on dying flames.
I traced the horizon instead. Observing landscape. Noting the contrast.
He touched the flag on his t-shirt. I adjusted my plain gray one.
The unpayable debt. The crumbling infrastructure. The forgotten manufacturing. The dependent supply chains. The devaluing currency.
The pendulum clock ticked. Relentless. Indifferent to empires.
His eyes said what his patriotism couldn't voice. Something fundamental breaking.
I'd seen this coming. Years traveling showed me. Different systems. Different values. American exceptionalism viewed from outside.
Pragmatism replaced my old idealism. See things as they are. Not as wished.
The logs shifted. Flames reached higher. Then lower. The cycle of fire.
Divergence
Society always splits during shifts.
Some adapt. Some don't.
Printing arrived. Scribes starved. Publishers thrived. Information accelerated. Readers multiplied. Ideas spread. Adapters prospered.
Steam engines came. Weavers died. Factory owners flourished. Villages emptied. Cities grew. Coal replaced farms. Railways replaced wagons. New skills meant survival.
Computers transformed everything. Typewriters vanished. Software boomed. Data replaced paper. Networks replaced cabinets. Programmers replaced typists. Digital skills determined success.
The self-reliant thrived in each transition. Those waiting for rescue fell behind.
Now AI reshapes creativity. Some artists resist. Some harness it. Gap widens daily.
Bitcoin offers refuge. Critics mock. Adopters build wealth. The distance grows.
Remote work redraws maps. Office-bound struggle. Location-free flourish.
The pendulum swings. Power shifts. Some rise with it. Some fall against it.
Two societies emerge. Adaptive. Resistant. Prepared. Pretending.
Advantage
Early adapters win. Not through genius. Through action.
First printers built empires. First factories created dynasties. First websites became giants.
Bitcoin followed this pattern. Laptop miners became millionaires. Early buyers became legends.
Critics repeat themselves: "Too volatile." "No value." "Government ban coming."
Doubters doubt. Builders build. Gap widens.
Self-reliance accelerates adaptation. No permission needed. No consensus required. Act. Learn. Build.
The burn pile flames like empire's glory. Bright. Consuming. Temporary.
Blindness
Our brains see tigers. Not economic shifts.
We panic at headlines. We ignore decades-long trends.
We notice market drops. We miss debt cycles.
We debate tweets. We ignore revolutions.
Not weakness. Just humanity. Foresight requires work. Study. Thought.
Self-reliant thinking means seeing clearly. No comforting lies. No pleasing narratives. Just reality.
The clock pendulum swings. Time passes regardless of observation.
Action
Empires fall. Families need security. Children need futures. Lives need meaning.
You can adapt faster than nations.
Assess honestly. What skills matter now? What preserves wealth? Who helps when needed?
Never stop learning. Factory workers learned code. Taxi drivers joined apps. Photographers went digital.
Diversify globally. No country owns tomorrow. Learn languages. Make connections. Stay mobile.
Protect your money. Dying empires debase currencies. Romans kept gold. Bitcoin offers similar shelter.
Build resilience. Grow food. Make energy. Stay strong. Keep friends. Read old books. Some things never change.
Self-reliance matters most. Can you feed yourself? Can you fix things? Can you solve problems? Can you create value without systems?
Movement
Humans were nomads first. Settlers second. Movement in our blood.
Our ancestors followed herds. Sought better lands. Survival meant mobility.
The pendulum swings here too. Nomad to farmer. City-dweller to digital nomad.
Rome fixed people to land. Feudalism bound serfs to soil. Nations created borders. Companies demanded presence.
Now technology breaks chains. Work happens anywhere. Knowledge flows everywhere.
The rebuild America seeks requires fixed positions. Factory workers. Taxpaying citizens in permanent homes.
But technology enables escape. Remote work. Digital currencies. Borderless businesses.
The self-reliant understand mobility as freedom. One location means one set of rules. One economy. One fate.
Many locations mean options. Taxes become predatory? Leave. Opportunities disappear? Find new ones.
Patriotism celebrates roots. Wisdom remembers wings.
My friend's boots dug into his soil. Planted. Territorial. Defending.
My Chucks rested lightly. Ready. Adaptable. Departing.
His toolshed held equipment to maintain boundaries. Fences. Hedges. Property lines.
My backpack contained tools for crossing them. Chargers. Adapters. Currency.
The burn pile flame flickers. Fixed in place. The spark flies free. Movement its nature.
During Rome's decline, the mobile survived best. Merchants crossing borders. Scholars seeking patrons. Those tied to crumbling systems suffered most.
Location independence means personal resilience. Economic downturns become geographic choices. Political oppression becomes optional suffering.
Technology shrinks distance. Digital work. Video relationships. Online learning.
Self-sovereignty requires mobility. The option to walk away. The freedom to arrive elsewhere.
Two more worlds diverge. The rooted. The mobile. The fixed. The fluid. The loyal. The free.
Hope
Not decline. Transition. Painful but temporary.
America may weaken. Humanity advances. Technology multiplies possibilities. Poverty falls. Knowledge grows.
Falling empires see doom. Rising ones see opportunity. Both miss half the picture.
Every shift brings destruction and creation. Rome fell. Europe struggled. Farms produced less. Cities shrank. Trade broke down.
Yet innovation continued. Water mills appeared. New plows emerged. Monks preserved books. New systems evolved.
Different doesn't mean worse for everyone.
Some industries die. Others birth. Some regions fade. Others bloom. Some skills become useless. Others become gold.
The self-reliant thrive in any world. They adapt. They build. They serve. They create.
Choose your role. Nostalgia or building.
The pendulum swings. East rises again. The cycle continues.
Fading
The burn pile dimmed. Embers fading. Night air cooling.
My friend's shoulders changed. Tension releasing. Something accepted.
His patriotism remained. His illusions departed.
The pendulum clock ticked steadily. Measuring more than minutes. Measuring eras.
Two coffee cups. His: military-themed, old and chipped but cherished. Mine: plain porcelain, new and unmarked.
His eyes remained on smoldering embers. Mine moved between him and the darkening trees.
His calendar marked local town meetings. Mine tracked travel dates.
The last flame flickered out. Spring peepers filled the silence.
In darkness, we watched smoke rise. The world changing. New choices ahead.
No empire lasts forever. No comfort in denial. Only clarity in acceptance.
Self-reliance the ancient answer. Build your skills. Secure your resources. Strengthen your body. Feed your mind. Help your neighbors.
The burn pile turned to ash. Empire's glory extinguished.
He stood facing his land. I faced the road.
A nod between us. Respect across division. Different strategies for the same storm.
He turned toward his home. I toward my vehicle.
The pendulum continued swinging. Power flowing east once more. Five centuries ending. Five centuries beginning.
"Bear in mind that everything that exists is already fraying at the edges." — Marcus Aurelius
Tomorrow depends not on nations. On us.
-
 @ 33633f1e:21137a92
2025-04-30 07:15:58
@ 33633f1e:21137a92
2025-04-30 07:15:58Toglobal learninghuwabohu – wer räumt das alles auf?
Einheit veröffentlicht am Oktober 9, 2024 von settle
Worum religlobalt
| | | |:---:|:---:| |
 |
|  |
|Die zweite Schöpfungserzählung / Kirchenwälder in Äthiopien / Bewahrung der Schöpfung
Wir alle leben auf einer Erde – Tiere, Pflanzen und Menschen. Am Anfang war die Erde wüst und leer … aus diesem anfänglichen Tohuwabohu schafft Gott die natürliche Ordnung der Welt. Ursprünglich, so erzählt es der erste Schöpfungshymnus, war alles gut, wenn auch aus menschlicher Sicht, ziemlich durcheinander.
In der zweiten Schöpfungserzählung setzt Gott den Menschen in einen Paradiesgarten. Dieser Mensch soll nun die Erde behüten und bewahren. Das bedeutet auch Platz zu schaffen und aufzuräumen. Menschen greifen gemäß ihrem Auftrag, den Garten zu bestellen, in die Natur ein. Welche Konsequenzen hat unser Handeln? Wie sieht es mit dem zweiten Teil des Auftrags aus, den Garten auch zu beschützen? Was bedeutet es, wenn Menschen anfangen “auszuräumen” und dabei die Konsequenzen nicht mitbedenken?
In diesem Unterrichtsentwurf lernen Schüler:innen die biblischen Schöpfungserzählungen kennen und setzen sich kritisch mit den Folgen des menschlichen Handelns für Klima und Umwelt auseinander. Beispielhaft werden die Brot für die Welt “Reli fürs Klima”-Projekte aufgenommen. Anhand von Projekten in Kirchenwäldern der orthodoxen Kirche in Äthiopien und in Kirchenwäldern in Brandenburg erfahren die Schülerinnen und Schüler praktische Möglichkeiten, den Auftrag Gottes an die Menschen, die Schöpfung zu bebauen und zu bewahren, ernst zu nehmen und umzusetzen. Wie kann richtiges Aufräumen aussehen?
Die Konzeption orientiert sich am Dreischritt „Erkennen –Begreifen – Handeln“:
- Erkennen: Und siehe, es war sehr gut … – Zugang zum 2. biblischen Schöpfungsbericht (Gen 2,4–15)
- Begreifen: Und machet sie euch untertan – zerstören wir die Erde?
- Handeln: Bestellen und beschützen – kleine Paradiesgärten
Für das Unterrichtsvorhaben werden mindestens 3 x 45 Minuten Unterrichtszeit veranschlagt. Alle drei Teile des Unterrichtes können auch deutlich vertiefter und mit größerem Zeiteinsatz und -aufwand durchgeführt werden.
Das vorgestellte Unterrichtsvorhaben wurde entwickelt im Rahmen des von Brot für die Welt geförderten Projektes “reliGlobal”. Zur Förderung des “Globalen Lernens” erstellen Mitarbeiter:innen aus mehreren Pädagogischen Instituten in der EKD kooperativ Unterrichtsmaterialien für den evangelischen Religionsunterricht.
Unterrichtsschritte
Tohuwabohu – Schritt 1 Erkennen
In diesem Schritt beschäftigen sich die Schüler:innen mit dem zweiten biblischen Schöpfungsbericht.
Tohuwabohu – Schritt 2 Begreifen
In diesem Schritt werden die Auswirkungen der Eingriffe des Menschen in die Natur ins Blickfeld genommen und problematisiert.
Tohuwabohu – Schritt 3 Handeln
In diesem Schritt lernen die Schüler:innen praktische Möglichkeiten, die Natur zu bewahren, kennen und selbst umzusetzen.
Metamaterial
Tohuwabohu – Theologisch-Didaktische Hinweise
Tohuwabohu – Curricularer Bezug
-
 @ e7454994:7bb2dac7
2025-04-29 16:28:59
@ e7454994:7bb2dac7
2025-04-29 16:28:59Imagine
According to Cazoomi, total revenue for nonprofits in the U.S. reached approximately $3.7 trillion in 2024.
I know in some cases a billion is a hundred million instead of a thousand million (presumably so that some millionaires can call themselves billionaires to distinguish themselves from the riffraff). But that’s not the case here. A trillion is one followed by 12 zeros, so in 2024, US non-profits’ expenses were
3,700,000,000,000 dollars.
How much is a trillion?
And that’s just the USA. We could safely double it for worldwide non-profits and still be well below the actual figure. To be conservative, let’s say 6 trillion of our dollars each year goes on the kinds of projects that non-profits are allowed to do (essentially, making the world a better place).
Think what you could do with just one million dollars. Now think of that times six million! The entire population of Congo, each man, woman, and child, could become a millionaire!. It’s not really imaginable.
That’s how much nonprofits have. What the hell have they done with all that money? In most places where poverty and malnutrition are rife, two thousand dollars a year per family would be more than enough to enable people to sort out whatever problems they have and convert their local community to abundance over three years. Six trillion divided by two thousand is three billion.
The people whom we allow to manage ‘aid’ for us are (to be polite) inept, and we need to bypass them urgently. Directsponsor.org and clickforcharity.net are part of a proof of concept, and our aim is to prove that a better way is possible by doing it.
When a hierarchy exists, it presents a focus of power that power-seeking individuals and cliques can over time turn to their advantage… Even volunteer organizations are subject to intrigues, power grabs, covert arrangements, misallocation of funds, etc. The problem is made worse by the fact that those who most desire power and who are the most ruthless are the very ones who tend to work their way to the top of hierarchies.
More Fun With Figures
Oxfam UK raised £368,000,000 in 2013-14. That’s around 450,000,000 euros. What could we do with that kind of money? A direct sponsorship project is, for a family, 120 per month = 1440 per year. 1440 / 450,000,000 = 312,500 families.
312,500 families, x 4 = 1,250,000 people, would move from poverty into abundance every 3 years with the money that goes through Oxfam. Does Oxfam achieve anything like this with our money?
Oxfam UK is just one of many, many such charities and is small fry when you look at things like USAID, which ran through 27 billion dollars in the year to 2025. What could we do with that?
Its well over 15 million families. Over 60 million people! Or, the entire population of Botswana, Namibia, Mauritania, Liberia, the Republic of Congo, the Central African Republic, Libya, Sierra Leone, Eritrea, Togo, and Guinea combined. This is only to make a point, not to suggest that we would ever achieve such numbers. It shows how wasteful and scandalous our present “aid” efforts really are.
NGOs and governments waste our money.
Solution

Until recently, it was impossible to send money directly to another human without going through the banking system. The big charity organisations were a necessary part of the process, and they made the most of their position. Think about it: you have a family to feed, rent or a mortgage that has to be paid, or you’ll be homeless and destitute. What would your priority be? Apart from the top level, these are generally good people with the best intentions.
But now we have Bitcoin. People can send money all over the world at extremely low cost. The recipients aren’t stupid; they know what they need better than any NGO “expert,” and any expertise or teaching they need, they can get if they have the money to pay for it. This way, the power relationship is reversed in favor of our recipients.
All we need is a system (open and distributed) that ensures sponsors’ funds are not being squandered and the projects being supported are not scams.
A few people decided to start such a project. We have a system almost fully built and currently being tested out. It will enable people to get together into small groups of sponsors to fund small, local projects by directly funding the individuals working on the project. Anything from a regular monthly commitment to a click-for-charity system where you don’t even need any money to occasional one-off purchases of items for a project will be possible.
Here’s our pilot project in Badilisha, on Lake Victoria.
If you like doing stuff on social media, please sign up on our beta site (no money needed) and say hi; we need a few people to get it started. clickforcharity.net.
-
 @ 6f50351f:7b36c393
2025-04-30 06:34:17
@ 6f50351f:7b36c393
2025-04-30 06:34:17Toglobal learninghuwabohu – wer räumt das alles auf?
Einheit veröffentlicht am Oktober 9, 2024 von settle
Worum religlobalt
| | | |:---:|:---:| |
 |
|  |
|Die zweite Schöpfungserzählung / Kirchenwälder in Äthiopien / Bewahrung der Schöpfung
Wir alle leben auf einer Erde – Tiere, Pflanzen und Menschen. Am Anfang war die Erde wüst und leer … aus diesem anfänglichen Tohuwabohu schafft Gott die natürliche Ordnung der Welt. Ursprünglich, so erzählt es der erste Schöpfungshymnus, war alles gut, wenn auch aus menschlicher Sicht, ziemlich durcheinander.
In der zweiten Schöpfungserzählung setzt Gott den Menschen in einen Paradiesgarten. Dieser Mensch soll nun die Erde behüten und bewahren. Das bedeutet auch Platz zu schaffen und aufzuräumen. Menschen greifen gemäß ihrem Auftrag, den Garten zu bestellen, in die Natur ein. Welche Konsequenzen hat unser Handeln? Wie sieht es mit dem zweiten Teil des Auftrags aus, den Garten auch zu beschützen? Was bedeutet es, wenn Menschen anfangen “auszuräumen” und dabei die Konsequenzen nicht mitbedenken?
In diesem Unterrichtsentwurf lernen Schüler:innen die biblischen Schöpfungserzählungen kennen und setzen sich kritisch mit den Folgen des menschlichen Handelns für Klima und Umwelt auseinander. Beispielhaft werden die Brot für die Welt “Reli fürs Klima”-Projekte aufgenommen. Anhand von Projekten in Kirchenwäldern der orthodoxen Kirche in Äthiopien und in Kirchenwäldern in Brandenburg erfahren die Schülerinnen und Schüler praktische Möglichkeiten, den Auftrag Gottes an die Menschen, die Schöpfung zu bebauen und zu bewahren, ernst zu nehmen und umzusetzen. Wie kann richtiges Aufräumen aussehen?
Die Konzeption orientiert sich am Dreischritt „Erkennen –Begreifen – Handeln“:
- Erkennen: Und siehe, es war sehr gut … – Zugang zum 2. biblischen Schöpfungsbericht (Gen 2,4–15)
- Begreifen: Und machet sie euch untertan – zerstören wir die Erde?
- Handeln: Bestellen und beschützen – kleine Paradiesgärten
Für das Unterrichtsvorhaben werden mindestens 3 x 45 Minuten Unterrichtszeit veranschlagt. Alle drei Teile des Unterrichtes können auch deutlich vertiefter und mit größerem Zeiteinsatz und -aufwand durchgeführt werden.
Das vorgestellte Unterrichtsvorhaben wurde entwickelt im Rahmen des von Brot für die Welt geförderten Projektes “reliGlobal”. Zur Förderung des “Globalen Lernens” erstellen Mitarbeiter:innen aus mehreren Pädagogischen Instituten in der EKD kooperativ Unterrichtsmaterialien für den evangelischen Religionsunterricht.
Unterrichtsschritte
Tohuwabohu – Schritt 1 Erkennen
In diesem Schritt beschäftigen sich die Schüler:innen mit dem zweiten biblischen Schöpfungsbericht.
Tohuwabohu – Schritt 2 Begreifen
In diesem Schritt werden die Auswirkungen der Eingriffe des Menschen in die Natur ins Blickfeld genommen und problematisiert.
Tohuwabohu – Schritt 3 Handeln
In diesem Schritt lernen die Schüler:innen praktische Möglichkeiten, die Natur zu bewahren, kennen und selbst umzusetzen.
Metamaterial
Tohuwabohu – Theologisch-Didaktische Hinweise
Tohuwabohu – Curricularer Bezug
-
 @ 61bf790b:fe18b062
2025-04-29 12:23:09
@ 61bf790b:fe18b062
2025-04-29 12:23:09In a vast digital realm, two cities stood side by side: the towering, flashing metropolis of Feedia, and the decentralized, quiet city of Nostra.
Feedia was loud—blinding, buzzing, and always on. Screens plastered every wall, whispering the latest trends into citizens’ ears. But in this city, what you saw wasn’t up to you. It was determined by a towering, unseen force known as The Algorithm. It didn’t care what was true, meaningful, or helpful—only what would keep your eyes glued and your attention sold.
In Feedia, discovery wasn’t earned. It was assigned.
And worse—there was a caste system. To have a voice, you needed a Blue Check—a glowing badge that marked you as “worthy.” To get one, you had to pay or play. Pay monthly dues to the high towers or entertain The Algorithm enough to be deemed “valuable.” If you refused or couldn’t afford it, your voice was cast into the noise—buried beneath outrage bait and celebrity screams.
The unmarked were like ghosts—speaking into the void while the checked dined in Algorithm-favored towers. It was a digital monarchy dressed up as a democracy.
Then, there was Nostra.
There were no glowing checkmarks in Nostra—just signal. Every citizen had a light they carried, one that grew brighter the more they contributed: thoughtful posts, reshared ideas, built tools, or boosted others. Discovery was based not on payment or privilege, but participation and value.
In Nostra, you didn’t rise because you paid the gatekeeper—you rose because others lifted you. You weren’t spoon-fed; you sought, you found, you earned attention. It was harder, yes. But it was real.
And slowly, some in Feedia began to awaken. They grew tired of being fed fast-food content and ignored despite their voices. They looked across the river to Nostra, where minds weren’t bought—they were built.
And one by one, they began to cross.
-
 @ 005bc4de:ef11e1a2
2025-04-29 16:08:56
@ 005bc4de:ef11e1a2
2025-04-29 16:08:56Trump Bitcoin Report Card - Day 100
For whatever reason day 100 of a president's term has been deemed a milestone. So, it's time to check in with President Trump's bitcoin pledges and issue a report card.
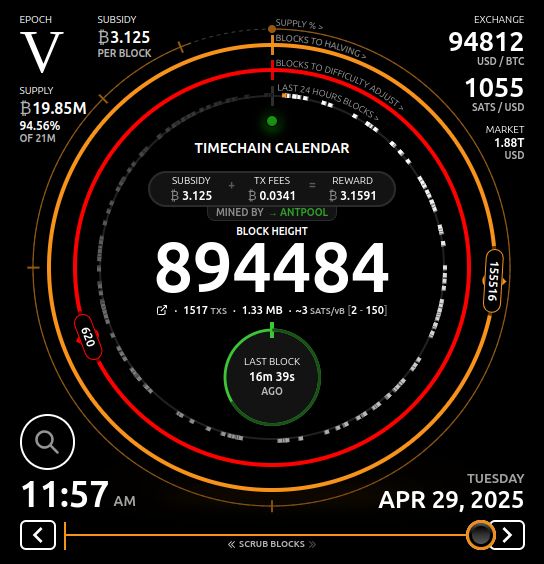
Repo and prior reports: - GitHub: https://github.com/crrdlx/trump-bitcoin-report-card - First post: https://stacker.news/items/757211 - Progress Report 1: https://stacker.news/items/774165 - Day 1 Report Card: https://stacker.news/items/859475 - Day 100 Report Card: https://stacker.news/items/966434
Report Card | | Pledge | Prior Grade | Current Grade | |--|--|--|--| | 1 | Fire SEC Chair Gary Gensler on day 1 | A | A | | 2 | Commute the sentence of Ross Ulbricht on day 1 | A | A | | 3 | Remove capital gains taxes on bitcoin transactions | F | F | | 4 | Create and hodl a strategic bitcoin stockpile | D | C- | | 5 | Prevent a CBDC during his presidency | B+ | A | | 6 | Create a "bitcoin and crypto" advisory council | C- | C | | 7 | Support the right to self-custody | D+ | B- | | 8 | End the "war on crypto" | D+ | B+ | | 9 | Mine all remaining bitcoin in the USA | C- | C | | 10 | Make the US the "crypto capital of the planet" | C- | C+ |
Comments
Pledge 1 - SEC chair - (no change from earlier) - Gensler is out. This happened after the election and Trump took office. With the writing on the wall, Gensler announced he would resign, Trump picked a new SEC head in Paul Atkins, and Gensler left office just before Trump was sworn in. The only reason an A+ was not awarded was that Trump wasn't given the chance to actually fire Gensler, because he quit. No doubt, though, his quitting was due to Trump and the threat of being sacked.
Day 100 Report Card Grade: A
Pledge 2 - free Ross - (no change from earlier) - Ross Ulbricht's sentence was just commuted. Going will "option 3" above, the pledge was kept. An A+ would have been a commutation yesterday or by noon today, but, let's not split hairs. It's done.
Day 100 Report Card Grade: A
Pledge 3 - capital gains - This requires either executive action and/or legislation. There was no action. Executive action can be done with the stroke of a pen, but it was not. Legislation is tricky and time-consuming, however, there wasn't even mention of this matter. This seems to be on the back burner since statements such as this report in November. See Progress Report 1: https://stacker.news/items/774165 for more context.
Trump's main tax thrust has been the tariff, actually a tax increase, instead of a cut. Currently, the emphasis is on extending the "Trump tax cuts" and recently House Speaker Mike Johnson indicated such a bill would be ready by Memorial Day. Earlier in his term, there was more chatter about tax relief for bitcoin or cryptocurrency. There seems to be less chatter on this, or none at all, such as its absence in the "ready by Memorial Day" article.
Until tax reform is codified and signed, it isn't tax law and the old code still applies.
Day 100 Report Card Grade: F
Pledge 4 - bitcoin reserve - The initial grade was a C, it was dropped to a D mainly due to Trump's propensity to [alt]coinery, and now it's back to a C-.
Getting the grade back up into C-level at a C- was a little bumpy. On March 2, 2025, Trump posted that a U.S. Crypto Reserve would be created. This is what had been hoped for, except that the pledge was for a Bitcoin Reserve, not crypto. And secondly, he specifically named XRP, SOL, and ADA (but not BTC). Just a couple of hours later, likely in clean up mode, he did add BTC (along with ETH) as "obviously" being included. So, the "Bitcoin Reserve" became a "Crypto Reserve."
Maybe still in "cleanup mode," Sec. of Commerce Howard Lutnick said bitcoin will hold "special status" in the reserve. Then, on March 6, an executive order made the U.S. Digital Asset Stockpile official. Again, "Bitcoin" was generalized until section 3 where the "Strategic Bitcoin Reserve" did come to official fruition.
The grade is only a C- because the only thing that happened was the naming of the stockpile. Indeed, it became official. But the "stockpile" was just BTC already held by the U.S. government. I think it's fair to say most bitcoiners would have preferred a statement about buying BTC. Other Trump bitcoin officials indicated acquiring "as much as we can get", which sounds great, but until it happens, is only words.
Day 100 Report Card Grade: C-
Pledge 5 - no CBDC - An executive order on January 23, 2025 forbade a CBDC in section 1, part v by "prohibiting the establishment, issuance, circulation, and use of a CBDC."
Day 100 Report Card Grade: A
Pledge 6 - advisory council - The Trump bitcoin or crypto team consists of the following: David Sacks as “crypto czar” and Bo Hines as executive director of the Presidential Council of Advisers for Digital Assets.
A White House Crypto Summit (see video) was held on March 7, 2025. In principle, the meeting was good, however, the summit seemed (a) to be very heavily "crypto" oriented, and (b) to largely be a meet-and-greet show.
Still, just the fact that such a show took place, inside the White House, reveals how far things have come and the change in climate. For the grade to go higher, more tangible things should take place over time.
Day 100 Report Card Grade: C
Pledge 7 - self-custody - There's been a bit of good news though on this front. First, the executive order above from January 23 stated in section 1, i, one of the goals was "...to maintain self-custody of digital assets." Also, the Phoenix wallet returned to the U.S. In 2024, both Phoenix and Wallet of Satoshi pulled out of the U.S. for fear of government crackdowns. The return of Phoenix, again, speaks to the difference in climate now and is a win for self-custody.
To rise above B-level, more assurance, it would be good to see further clear assurance that people can self-custody, that developers can build self-custody, and businesses can create products to self-custody. Also, Congressional action could get to an A.
Day 100 Report Card Grade: B-
Pledge 8 - end war on crypto - There has been improvement here. First, tangibly, SAB 121 was sent packing as SEC Commissioner Hester Peirce announced. Essentially, this removed a large regulatory burden. Commissioner Peirce also said ending the burdens will be a process to get out of the "mess". So, there's work to do. Also, hurdles were recently removed so that banks can now engage in bitcoin activity. This is both a symbolic and real change.
Somewhat ironically, Trump's own venture into cryptocurrency with his World Liberty Financial and the $TRUMP and $MELANIA tokens, roundly poo-pood by bitcoiners, might actually be beneficial in a way. The signal from the White House seems to be on all things cryptocurrency, "Do it."
The improvement and climate now seems very different than with the previous administration and leaders who openly touted a war on crypto.
Day 100 Report Card Grade: B+
Pledge 9 - USA mining - As noted earlier, this is an impossible pledge. That said, things can be done to make America mining friendly. The U.S. holds an estimated 37 to 40% of Bitcoin hash rate, which is substantial. Plus, Trump, or the Trump family at least, has entered into bitcoin mining. With Hut 8, Eric Trump is heading "American Bitcoin" to mine BTC. Like the $TRUMP token, this conveys that bitcoin mining is a go in the USA.
Day 100 Report Card Grade: C
Pledge 10 - USA crypto capital - This pledge closely aligned with pledges 8 and 9. If the war on crypto ends, the USA becomes more and more crypto and bitcoin friendly. And, if the hashrate stays high and even increases, that puts the USA at the center of it all. Most of the categories above have seen improvements, all of which help this last pledge. Trump's executive orders help this grade as well as they move from only words spoken to becoming official policy.
To get higher, the Bitcoin Strategic Reserve should move from a name-change only to acquiring more BTC. If the USA wants to be the world's crypto capital, being the leader in bitcoin ownership is the way to do it.
Day 100 Report Card Grade: C+
Sources
- Nashville speech - https://www.youtube.com/watch?v=EiEIfBatnH8
- CryptoPotato "top 8 promises" - https://x.com/Crypto_Potato/status/1854105511349584226
- CNBC - https://www.cnbc.com/2024/11/06/trump-claims-presidential-win-here-is-what-he-promised-the-crypto-industry-ahead-of-the-election.html
- BLOCKHEAD - https://www.blockhead.co/2024/11/07/heres-everything-trump-promised-to-the-crypto-industry/
- CoinTelegraph - https://cointelegraph.com/news/trump-promises-crypto-election-usa
- China vid - Bitcoin ATH and US Strategic Bitcoin Stockpile - https://njump.me/nevent1qqsgmmuqumhfktugtnx9kcsh3ap6v7ca4z8rgx79palz2qk0wzz5cksppemhxue69uhkummn9ekx7mp0qgszwaxc8j8e0zw9sdq59y43rykyx3wm0lcd2502xth699v0gxf0degrqsqqqqqpglusv6
- Capitals gains tax - https://bravenewcoin.com/insights/trump-proposes-crypto-tax-cuts-targets-u-s-made-tokens-for-tax-exemption Progress report 1 ------------------------------------------------------------------------------------
- Meeting with Brian Armstrong - https://www.wsj.com/livecoverage/stock-market-today-dow-sp500-nasdaq-live-11-18-2024/card/exclusive-trump-to-meet-privately-with-coinbase-ceo-brian-armstrong-DDkgF0xW1BW242rVeuqx
- Michael Saylor podcast - https://fountain.fm/episode/DHEzGE0f99QQqyM36nVr
- Gensler resigns - https://coinpedia.org/news/big-breaking-sec-chair-gary-gensler-officially-resigns/ Progress report 2 ------------------------------------------------------------------------------------
- Trump & Justin Sun - https://www.coindesk.com/business/2024/11/26/justin-sun-joins-donald-trumps-world-liberty-financial-as-adviser $30M investment: https://www.yahoo.com/news/trump-crypto-project-bust-until-154313241.html
- SEC chair - https://www.cnbc.com/2024/12/04/trump-plans-to-nominate-paul-atkins-as-sec-chair.html
- Crypto czar - https://www.zerohedge.com/crypto/trump-names-david-sacks-white-house-ai-crypto-czar
- Investigate Choke Point 2.0 - https://www.cryptopolitan.com/crypto-czar-investigate-choke-point/
- Crypto council head Bo Hines - https://cointelegraph.com/news/trump-appoints-bo-hines-head-crypto-council
- National hash rate: https://www.cryptopolitan.com/the-us-controls-40-of-bitcoins-hashrate/
- Senate committee https://coinjournal.net/news/rep-senator-cynthia-lummis-selected-to-chair-crypto-subcommittee/
- Treasurh Sec. CBDC: https://decrypt.co/301444/trumps-treasury-pick-scott-bessant-pours-cold-water-on-us-digital-dollar-initiative
- National priority: https://cointelegraph.com/news/trump-executive-order-crypto-national-priority-bloomberg?utm_source=rss_feed&utm_medium=rss&utm_campaign=rss_partner_inbound
- $TRUMP https://njump.me/nevent1qqsffe0d7mgtu5jhasy4hmkcdy7wfrlcqwc4vf676hulvdn8uaqa3acpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyztpa8q038vw5xluyhnydj5u39d7cpssvuswjhhjqj8q42jh4ul3wqcyqqqqqqgmha026
- World Liberty buys alts: https://www.theblock.co/post/335779/trumps-world-liberty-buys-25-million-of-tokens-including-link-tron-aave-and-ethena?utm_source=rss&utm_medium=rss
- CFTC chair: https://cryptoslate.com/trump-appoints-crypto-advocate-caroline-pham-as-cftc-acting-chair/
- WLF buys wrapped BTC https://www.cryptopolitan.com/trump-buys-47-million-in-bitcoin/
- SEC turnover https://www.theblock.co/post/335944/trump-names-sec-commissioner-mark-uyeda-as-acting-chair-amid-a-crypto-regulatory-shift?utm_source=rss&utm_medium=rss
- ----------------------------100 Days Report---------------------------------Davos speech "world capital of AI and crypto" https://coinpedia.org/news/big-breaking-president-trump-says-u-s-to-become-ai-and-crypto-superpower/
- SAB 121 gone, Hester P heads talk force & ends sab 121?, war on crypto https://x.com/HesterPeirce/status/1882562977985114185 article: https://www.theblock.co/post/336761/days-after-gensler-leaves-sec-rescinds-controversial-crypto-accounting-guidance-sab-121?utm_source=twitter&utm_medium=social CoinTelegraph: https://cointelegraph.com/news/trump-executive-order-cbdc-ban-game-changer-us-institutional-crypto-adoption?utm_source=rss_feed&utm_medium=rss&utm_campaign=rss_partner_inbound
- Possible tax relief https://cryptodnes.bg/en/will-trumps-crypto-policies-lead-to-tax-relief-for-crypto-investors/
- War on crypto https://decrypt.co/304395/trump-sec-crypto-task-force-priorities-mess
- Trump "truths" 2/18 make usa #1 in crypto, "Trump effect" https://www.theblock.co/post/333137/ripple-ceo-says-75-of-open-roles-are-now-us-based-due-to-trump-effect and https://www.coindesk.com/markets/2025/01/06/ripples-garlinghouse-touts-trump-effect-amid-bump-in-u-s-deals
- Strategic reserve https://njump.me/nevent1qqsf89l74mqfkk74jqhjcqtwp5m970gedmtykn5uhl0vz9mhmrvvvgqpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyztpa8q038vw5xluyhnydj5u39d7cpssvuswjhhjqj8q42jh4ul3wqcyqqqqqqge7c74u and https://njump.me/nevent1qqswv50m7mc95m3saqce08jzpqc0vedw4avdk6zxy9axrn3hqet52xgpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyztpa8q038vw5xluyhnydj5u39d7cpssvuswjhhjqj8q42jh4ul3wqcyqqqqqqgpc7cp3
- Strategic reserve, bitcoin special https://www.thestreet.com/crypto/policy/bitcoin-to-hold-special-status-in-u-s-crypto-strategic-reserve
- Bitcoin reserve, crypto stockpile https://decrypt.co/309032/president-trump-signs-executive-order-to-establish-bitcoin-reserve-crypto-stockpile vid link https://njump.me/nevent1qqs09h58patpv9vfjpcss6v5nxv7m23u8g6g43nqvkjzgzescztucmspr9mhxue69uhhyetvv9ujumt0d4hhxarj9ecxjmnt9upzqtjzyy2ylrsceh5uj20j5e95v0e99s3epsvyctu2y0vrwyltvq33qvzqqqqqqyus4pu7
- Truth summit https://njump.me/nevent1qqswj6sv0wr4d4ppwzam5egr5k6nmqgjpwmsrlx2a7d4ndpfj0fxvcqpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyztpa8q038vw5xluyhnydj5u39d7cpssvuswjhhjqj8q42jh4ul3wqcyqqqqqqgu0mzzh and vid https://njump.me/nevent1qqsptn8c8wyuhlqtjr5u767x20q4dmjvxy28cdj30t4v9phhf6y5a5spzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyztpa8q038vw5xluyhnydj5u39d7cpssvuswjhhjqj8q42jh4ul3wqcyqqqqqqgqklklu
- SEC chair confirmed https://beincrypto.com/sec-chair-paul-atkins-confirmed-senate-vote/
- pro bitcoin USA https://coinpedia.org/news/u-s-secretary-of-commerce-howard-lutnick-says-america-is-ready-for-bitcoin/
- tax cuts https://thehill.com/homenews/house/5272043-johnson-house-trump-agenda-memorial-day/
- "as much as we can get" https://cryptobriefing.com/trump-bitcoin-acquisition-strategy/
- ban on CBDC https://www.whitehouse.gov/presidential-actions/2025/01/strengthening-american-leadership-in-digital-financial-technology/
- Phoenix WoS leave https://www.coindesk.com/opinion/2024/04/29/wasabi-wallet-and-phoenix-leave-the-us-whats-next-for-non-custodial-crypto
- Trump hut 8 mining https://www.reuters.com/technology/hut-8-eric-trump-launch-bitcoin-mining-company-2025-03-31/
-
 @ 1b939fa8:1ebdc679
2025-04-29 11:57:05
@ 1b939fa8:1ebdc679
2025-04-29 11:57:05All of my outfit conversion mods and Nora's Commonwealth Reconstruction Project have requirements that are on Nexus and nowhere else. Exception for the outfit conversions is Devious Devices which is noted and links provided to Lovers Lab and other requirements. My mods are dependent on those original mods to work. If/when the originals come to DEG then I will update and remove the Nexus links in my descriptions.
-
 @ 502ab02a:a2860397
2025-04-30 02:51:33
@ 502ab02a:a2860397
2025-04-30 02:51:3350by40 คืออีกโครงการนึงที่ขยายภาพรวมขึ้นมาอีก recap กันครับ (ใครที่มาเจอกลางทาง อาจต้องย้อนเยอะครับ ย้อนไปสัก ปลายเดือน มีนาคม 2025) หลังจากที่เราได้ดูส่วนเล็กกันมาหลายตอน ตั้งแต่เรื่องเล็กๆอย่าง น้ำมันมะกอกปลอม ซึ่งตอนนั้นหลายคนที่อ่านอาจคิดว่า ไกลตัวส่วนใหญ่ยังดีพอ แต่ความนัยที่ซ่อนไว้ในบทนั้นคือ จุดเริ่มของการทำลายความเชื่อใจในอาหาร , ที่มาของบรอกโคลีเพื่อให้รู้ว่า สิ่งที่คิดว่าธรรมชาติ มันไม่ธรรมชาติ, นมโอ้ต นมประดิษฐ์ที่เป็นจุดที่เราคิดว่ามันคือการพลิกวงการแล้ว, การแอบจดสิทธิบัตรเมล็ดพันธุ์ที่เคยปลูกกินอย่างอิสระ, การพัฒนา GMO 2.0 ที่ไม่ต้องเรียกว่า GMO, โปรตีนจากแลป มาจนถึงเวย์ที่ไม่มีวัว แล้วเราก็ขยายภาพขึ้นกับข้อกำหนดการควบคุมการปลูกพืช UPOV1991/CPTPP, การเข้าสู่โรงเรียน, การกำเนิดของ ProVeg แล้วเราก็ได้รู้จักกับ Sebastian Joy ก็ถือว่าเดินทางมา 1 ด่านแล้วครับ หนทางเรื่องนี้ยังอีกยาวไกล วันนี้เราก็มาคุยกันถึงเรื่อง
โครงการ 50by40
โครงการนี้เริ่มต้นขึ้นในเดือนเมษายน ปี 2018 โดยมีการจัดการประชุม "50by40 Corporate Outreach Summit" ระหว่างวันที่ 27–29 เมษายน 2018 ที่กรุงเบอร์ลิน ประเทศเยอรมนี ซึ่งจัดโดย ProVeg International ร่วมกับ Humane Society of the United States การประชุมนี้ถือเป็นจุดเริ่มต้นของพันธมิตรระดับโลกที่มีเป้าหมายร่วมกันในการลดการผลิตและบริโภคผลิตภัณฑ์จากสัตว์ลง 50% ภายในปี 2040
Sebastian Joy ผู้ก่อตั้งและประธานของ ProVeg International มีบทบาทสำคัญในการริเริ่มโครงการ 50by40 โดยเขาได้ช่วยก่อตั้งพันธมิตรนี้เพื่อส่งเสริมการเปลี่ยนแปลงระบบอาหารโลก นอกจากนี้ ProVeg International ยังมีบทบาทในการสนับสนุนองค์กรและสตาร์ทอัพที่มุ่งเน้นการเปลี่ยนแปลงระบบอาหารผ่านโปรแกรมต่างๆ
แม้ว่าโครงการ 50by40 จะประกาศเป้าหมายในการลดการบริโภคผลิตภัณฑ์จากสัตว์เพื่อสุขภาพและสิ่งแวดล้อม แต่เบื้องหลังยังมีการดำเนินงานที่มุ่งเน้นการเปลี่ยนแปลงระบบอาหารโลก โดยการส่งเสริม "อาหารที่เพาะเลี้ยงในห้องปฏิบัติการเป็นหลัก"
โครงการนี้ยังมีการจัดกิจกรรมเพื่อดึงดูดนักลงทุนและผู้สนับสนุนทางการเงิน เช่น การจัดงาน Food Funders Circle ซึ่งเป็นเวทีสำหรับนักลงทุนที่สนใจในอาหารทางเลือก นอกจากนี้ โครงการ 50by40 ยังมีความสัมพันธ์กับองค์กรต่างๆ ทั้งภาครัฐและเอกชน รวมถึงองค์กรระดับนานาชาติ เช่น Greenpeace, WWF และ Compassion in World Farming ซึ่งมีเป้าหมายร่วมกันในการลดการบริโภคผลิตภัณฑ์จากสัตว์ และ ProVeg International เองก็มีสถานะเป็นผู้สังเกตการณ์ถาวรในองค์การสหประชาชาติ เช่น UNFCCC, IPCC และ CBD รวมถึงมีสถานะที่ปรึกษาพิเศษกับ ECOSOC และได้รับการรับรองจาก UNEA อีกด้วย ถ้ามองแค่เนทเวิร์คเบื้องต้นแล้ว วินาทีนี้ ตอบได้เลยครับว่า "อาหารที่เพาะเลี้ยงในห้องปฏิบัติการเป็นหลัก" มาแน่นอนครับ มองข้ามความ plant based / animal based ได้เลย
เพื่อบรรลุเป้าหมายนี้ โครงการได้ดำเนินกิจกรรมต่างๆ ทั้งในระดับโรงเรียนและการผลักดันนโยบายสาธารณะ ผมจะลองแบ่งเป็นข้อๆให้เพื่อความสะดวกในการมองภาพรวมประมาณนี้นะครับ
การดำเนินงานในโรงเรียนและเยาวชน 1. Early Action Network โครงการนี้เป็นความร่วมมือระหว่าง 50by40, ProVeg International และ Educated Choices Program โดยมีเป้าหมายในการส่งเสริมการบริโภคอาหารจากพืชในกลุ่มเด็กและเยาวชนผ่านกิจกรรมต่างๆ เช่น การจัดกิจกรรมเชิงโต้ตอบเกี่ยวกับสุขภาพ สิ่งแวดล้อม และสวัสดิภาพสัตว์, การจัดแคมเปญในโรงเรียนและชุมชน, การเผยแพร่สื่อการเรียนรู้และโปรแกรมฝึกอบรม, การปรับปรุงเมนูอาหารในโรงเรียนให้มีทางเลือกจากพืชมากขึ้น
โครงการนี้มุ่งหวังที่จะสร้างความตระหนักรู้และเปลี่ยนแปลงพฤติกรรมการบริโภคของเยาวชนตั้งแต่เนิ่นๆ เพื่อส่งเสริมการบริโภคอาหารที่ยั่งยืนและเป็นมิตรกับสิ่งแวดล้อม
- School Plates Programme ProVeg International ได้เปิดตัวโครงการ School Plates ในสหราชอาณาจักรเมื่อปี 2018 โดยมีเป้าหมายในการปรับปรุงเมนูอาหารในโรงเรียนให้มีความหลากหลายและสุขภาพดีขึ้นผ่านการเพิ่มทางเลือกอาหารจากพืช โครงการนี้ได้ร่วมมือกับโรงเรียน หน่วยงานท้องถิ่น และบริษัทจัดเลี้ยง เพื่อเปลี่ยนแปลงเมนูอาหารในโรงเรียนกว่า 3.1 ล้านมื้อจากอาหารที่มีเนื้อสัตว์เป็นหลักไปเป็นอาหารจากพืช
สำหรับในส่วนของการผลักดันนโยบายสาธารณะและการมีส่วนร่วมในเวทีนานาชาตินั้น ก็มีไม่น้อยครับ อาทิเช่น การมีส่วนร่วมในองค์การสหประชาชาติ ProVeg International มีสถานะเป็นผู้สังเกตการณ์ถาวรในองค์การสหประชาชาติ เช่น UNFCCC และ UNEP และได้มีบทบาทในการผลักดันให้มีการรวมประเด็นเกี่ยวกับอาหารจากพืชในการเจรจาด้านสภาพภูมิอากาศ โดยในปี 2022 ProVeg ได้เข้าร่วมการประชุมสภาพภูมิอากาศของสหประชาชาติในสตอกโฮล์มและบอนน์ เพื่อส่งเสริมแนวคิด "Diet Change Not Climate Change" และเรียกร้องให้มีการเปลี่ยนแปลงระบบอาหารสู่การบริโภคอาหารจากพืชมากขึ้น
การสนับสนุนเยาวชนในเวทีนานาชาติ ProVeg ได้จัดตั้ง Youth Board ซึ่งประกอบด้วยเยาวชนจากทั่วโลก เพื่อมีส่วนร่วมในการผลักดันนโยบายด้านอาหารจากพืชในเวทีสหประชาชาติ และเตรียมความพร้อมสำหรับการประชุม COP30 ที่จะจัดขึ้นในเบเลง ประเทศบราซิล
นอกจากนี้ยังมีการสนับสนุนองค์กรและสตาร์ทอัพที่มุ่งเปลี่ยนแปลงระบบอาหารอีกมากมาย โดยที่โดดเด่นเป็นพิเศษคือ โปรแกรม Kickstarting for Good ProVeg International ได้เปิดตัวโปรแกรม Kickstarting for Good ซึ่งเป็นโปรแกรมบ่มเพาะและเร่งการเติบโตสำหรับองค์กรไม่แสวงหาผลกำไร โครงการที่มีผลกระทบ และสตาร์ทอัพทางสังคมที่มุ่งเปลี่ยนแปลงระบบอาหาร โปรแกรมนี้มีระยะเวลา 8 สัปดาห์ โดยมีการฝึกอบรมแบบเข้มข้น การให้คำปรึกษาจากผู้เชี่ยวชาญ และโอกาสในการสร้างเครือข่าย เพื่อสนับสนุนการพัฒนาโครงการที่มีศักยภาพในการลดการบริโภคผลิตภัณฑ์จากสัตว์และส่งเสริมอาหารจากพืช
นอกจาก Sebastian Joy จะเริ่มต้นโครงการต่างๆมากมายไม่ว่าจะ ProVeg International, ProVeg Incubator, Kickstarting for Good แต่ก็ยังมี องค์กรพันธมิตรในเครือข่าย 50by40 ที่หลากหลาย เช่น Plant Powered Metro New York, Public Justice, Rainforest Alliance, Real Food Systems, Reducetarian Foundation, Rethink Your Food, SEED และ Seeding Sovereignty ซึ่งร่วมกันส่งเสริมการบริโภคอาหารจากพืชและการลดการบริโภคผลิตภัณฑ์จากสัตว์ แม้ว่าโครงการ 50by40 จะได้รับการสนับสนุนจากองค์กรต่างๆ อย่างกว้างขวาง แต่ยังไม่มีข้อมูลที่ชัดเจนเกี่ยวกับบริษัทเอกชนรายใดที่แสดงการสนับสนุนโครงการนี้อย่างเปิดเผยครับ
ทีนี้เรามาดูความเคลื่อนไหวของลูกพี่ใหญ่อย่าง USDA กันบ้างนะครับ จากการตรวจสอบข้อมูลที่มีอยู่จนถึงปัจจุบัน ยังไม่พบหลักฐานชัดเจนว่า กระทรวงเกษตรสหรัฐฯ (USDA) มีการสนับสนุนโครงการ 50by40 อย่างเป็นทางการหรือเปิดเผย อย่างไรก็ตาม มีความเคลื่อนไหวที่เกี่ยวข้องกับการส่งเสริมโปรตีนทางเลือกและการลดการบริโภคเนื้อสัตว์ในระดับนโยบายของสหรัฐฯ ซึ่งอาจสอดคล้องกับเป้าหมายของโครงการ 50by40 อยู่เช่นกันครับ
ในปี 2021 คณะกรรมาธิการด้านการเกษตรของสภาผู้แทนราษฎรสหรัฐฯ ได้สนับสนุนให้ USDA จัดสรรงบประมาณ 50 ล้านดอลลาร์สหรัฐฯ ผ่านโครงการ Agriculture and Food Research Initiative (AFRI) เพื่อสนับสนุนการวิจัยเกี่ยวกับโปรตีนทางเลือก เช่น การใช้พืช การเพาะเลี้ยงเซลล์ และการหมัก เพื่อพัฒนาอาหารที่มีคุณสมบัติคล้ายเนื้อสัตว์
นอกจากนี้ USDA ได้ยอมรับคำว่า "cell-cultured" เป็นคำที่ใช้เรียกเนื้อสัตว์ที่ผลิตจากการเพาะเลี้ยงเซลล์ในห้องปฏิบัติการ ซึ่งเป็นส่วนหนึ่งของการกำหนดมาตรฐานและการควบคุมผลิตภัณฑ์อาหารใหม่ๆ ที่เกี่ยวข้องกับโปรตีนทางเลือก
แล้วกลุ่มองค์กรด้านสิ่งแวดล้อมและสุขภาพ เช่น Center for Biological Diversity ได้ส่งจดหมายถึงรัฐมนตรีกระทรวงเกษตรสหรัฐฯ เรียกร้องให้ USDA นำประเด็นการลดการบริโภคเนื้อสัตว์และผลิตภัณฑ์นมมาเป็นส่วนหนึ่งของยุทธศาสตร์ด้านสภาพภูมิอากาศ และปรับปรุงแนวทางโภชนาการแห่งชาติให้สอดคล้องกับเป้าหมาย "ด้านความยั่งยืน"
แม้ว่า USDA จะไม่ได้แสดงการสนับสนุนโครงการ 50by40 โดยตรง แต่มีความร่วมมือกับองค์กรที่มีเป้าหมายคล้ายคลึงกัน เช่น ProVeg International และ The Good Food Institute ซึ่งเป็นพันธมิตรในเครือข่ายของ 50by40 โดยมีเป้าหมายในการส่งเสริมการบริโภคอาหารจากการเพาะเลี้ยงเซลล์ในห้องปฏิบัติการและโปรตีนทางเลือก
อนาคตได้มีการขีด Goal ไว้ประมาณนี้ เรายังคิดว่าการที่ "แค่ไม่กินมัน" "ก็แค่เลือกกินอาหารธรรมชาติ" จะยังเป็นคำพูดที่เราพูดได้อีกไหม สิ่งนี้ก็ยังเป็นคำถามต่อไปครับ คงไม่มีใครสามารถตอบได้ใน วันนี้ (มั๊ง)
แต่ที่แน่ๆ มีคนไม่น้อยแล้วแหละครับ ที่บอกว่าอาหารจากแลปคุมในโรงงานที่สะอาด มันก็ดีนี่ สะอาดปลอดภัย ดีกว่าเนื้อหมูที่ผัดข้างทาง ล้างหรือเปล่าก็ไม่รู้ เอาหมูแบบไหนมาก็ไม่รู้
มันดูเหมือนว่าเป็นการเปรียบเปรยแบบตรรกะวิบัตินะครับ แต่รอบตัวคุณ มีคนคิดแบบนี้เยอะไหม? เป็นคำถามที่ไม่มีคำตอบอีกเช่นกันครับ
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ d1667293:388e7004
2025-04-29 16:00:19
@ d1667293:388e7004
2025-04-29 16:00:19The "Bitcoindollar" system—an emerging term which describes the interplay of U.S. dollar-denominated stablecoins and Bitcoin as complementary forces in the evolving monetary framework of the digital era (and which replaces the defunct Petrodollar system)—has sparked an interesting debate on Nostr with PowMaxi.
You will find the thread links at the bottom of this article.
Powmaxi argues that attempting to merge hard money (Bitcoin) with soft money (the U.S. dollar) is structurally doomed, because the systems are inherently contradictory and cannot coexist without one eventually destroying the other.
This critique is certainly valid, but ONLY if the Bitcoindollar is viewed as a final system. But I never claim that. To the contrary, the conclusion in my book is that this is a system that buys time for fiat, absorbs global demand for monetary stability, and ushers in a Bitcoinized world without the immediate collapse and the reset of the fiat system which would otherwise cause dramatic consequences. The Bitcoindollar is the only way to a gradual Bitcoin dominance in 10-20 years time while avoiding sudden collapse of the fiat system, so that also the power elites who hold the keys to this system can adapt.\ At least this is my hope.
Therefore the "fusion" isn't the future. The siphoning is. And the U.S. may try to ride it as long as possible. The Bitcoindollar system is a transitional strategic framework, not a\ permanent monetary equilibrium. In the end I agree with PowMaxi.
His detailed critique deserves an equally detailed analysis. Here's how the objections break down and why they don’t necessarily undermine the Bitcoindollar system.
1. Hard Money vs. Soft Money: Opposed Systems?
Objection: Bitcoin is a closed, decentralized system with a fixed supply; the dollar is an open, elastic system governed by central banks and political power. These traits are mutually exclusive and incompatible.
Response: Ideologically, yes. Practically, no. Hybrid financial systems are not uncommon. Bitcoin and stablecoins serve different user needs: Bitcoin is a store of value; stablecoins are mediums of exchange. Their coexistence mirrors real-world economic needs. The contradiction can be managed, and is not fatal at least for the transitional phase.
2. Scarcity vs. Elasticity: Economic Incompatibility?
Objection: Bitcoin can’t inject liquidity in crises; fiat systems can. Anchoring fiat to Bitcoin removes policymakers' tools.
Response: Correct — but that’s why Bitcoin is held as a reserve, not used as the primary medium of exchange in the Bitcoindollar model. Fiat-based liquidity mechanisms still function via stablecoins, while Bitcoin acts as a counterweight to long-term monetary debasement. The system’s strength is in its optionality: you don’t have to use Bitcoin until you want an exit ramp from fiat.
3. No Stable Equilibrium: One Must Win?
Objection: The system will destabilize. Either Bitcoin undermines fiat or fiat suppresses Bitcoin.
Response: Not necessarily in this transitional phase. The “conflict” isn’t between tools — it’s between control philosophies. The dollar won’t disappear overnight, and Bitcoin isn’t going away. The likely outcome is a gradual shifting of savings and settlement layers to Bitcoin, while fiat continues to dominate day-to-day payments and credit markets — until Bitcoin becomes structurally better in both.
4. Gresham’s and Thiers’ Law: Hollowing Fiat?
Objection: People save in Bitcoin and spend fiat, eroding fiat value.
Response: Yes — and that’s been happening since 2009. But this isn’t a flaw; it’s a transition mechanism. The Bitcoindollar model recognizes this and creates a bridge: it monetizes U.S. debt while preserving access to hard money. In the long run, my expectation is that naturally bitcoin will prevail both as a SOV and currency, but until then, stablecoins and T-bill-backed tokens serve useful roles in the global economy.
5. Philosophical Incompatibility?
Objection: Bitcoin prioritizes individual sovereignty; fiat systems are hierarchical. They can't be reconciled.
Response: They don’t need to be reconciled ideologically to function in parallel. Users choose the tool that suits their needs. One empowers individual autonomy; the other offers state-backed convenience. This is a competition of values, not a mechanical incompatibility. The Bitcoindollar model is a strategy. It’s a bridge between old and new systems, not a permanent coexistence.
6. Fusion is Impossible?
Objection: It’s only a temporary bridge. One side must lose.
Response: Exactly. The Bitcoindollar system is a transitional bridge. But that doesn’t reduce its value. It provides a functional pathway for individuals, companies, and governments to gradually exit broken monetary systems and experiment with new models.
In the meantime, the U.S. benefits from stablecoin-driven Treasury demand, while Bitcoin continues to grow as a global reserve asset.
Bottom line: A Strategic Convergence, Not a Permanent Fusion
The Bitcoindollar system isn’t a contradiction. It’s a convergence zone. It reflects the reality that monetary systems evolve gradually, not cleanly. Bitcoin and fiat will compete, overlap, and influence each other. Eventually, yes — hard money wins. But until then, hybrid systems offer powerful stepping stones.
Thread links:
Thread started from this initial post.
-
 @ dc814bb0:7a410cb5
2025-04-29 23:09:50
@ dc814bb0:7a410cb5
2025-04-29 23:09:50hallo welt
[[ ]] Add as many elements as you want? [[X]] The X marks the correct answer! [[ ]] ... this is wrong ... [[X]] ... this has to be selected too ...
-
 @ 6c67a3f3:b0ebd196
2025-04-29 11:28:01
@ 6c67a3f3:b0ebd196
2025-04-29 11:28:01On Black-Starting the United Kingdom
In the event of a total failure of the electric grid, the United Kingdom would face a task at once technical and Sisyphean: the so-called black start — the reawakening of the nation’s darkened arteries without any external supply of power. In idealized manuals, the task is rendered brisk and clean, requiring but a few days' labor. In the world in which we live, it would be slower, more uncertain, and at times perilously close to impossible.
Let us unfold the matter layer by layer.
I. The Nature of the Undertaking
A black start is not a mere throwing of switches, but a sequential ballet. Small generating stations — diesel engines, hydro plants, gas turbines — must first breathe life into cold transmission lines. Substations must be coaxed into readiness. Load must be picked up cautiously, lest imbalance bring the whole effort to naught. Islands of power are stitched together, synchronized with exquisite care.
Each step is fraught with fragility. An unseen misalignment, an unsignaled overload, and hours of labor are lost.
II. The Dream of the Engineers
In theory, according to the National Grid Electricity System Operator (ESO), the sequence would unfold thus: within half a day, core transmission lines humming; within a day or two, hospitals lit and water flowing; within three days, cities reawakened; within a week, the nation, broadly speaking, restored to life.
This vision presupposes a fantasy of readiness: that black-start units are operational and plentiful; that communications systems, so delicately dependent on mobile networks and the internet, endure; that personnel, trained and coordinated, are on hand in sufficient numbers; and that no sabotage, no accident, no caprice of nature interrupts the dance.
III. The Real Order of Things
Reality is more obstinate. Many black-start capable plants have been shuttered in the name of efficiency. The financial incentives once offered to private generators for black-start readiness were judged insufficient; the providers withdrew.
Grid operations now rely on a lattice of private interests, demanding slow and complicated coordination. Telecommunications are vulnerable in a deep blackout. The old hands, steeped in the tacit lore of manual restoration, have retired, their knowledge scattered to the four winds. Cyber vulnerabilities have multiplied, and the grid’s physical inertia — the very thing that grants a system grace under perturbation — has grown thin, leaving the UK exposed to sudden collapses should synchronization falter.
Under such conditions, the best of hopes might yield five to ten days of partial recovery. Weeks would be required to restore the former web of normalcy. In certain cases — in the face of physical damage to high-voltage transformers, whose replacements take months if not years — black-start might founder altogether.
IV. The Quiet Admissions of Officialdom
In its polite documents, the National Grid ESO speaks carefully: essential services might see restoration within three days, but full public service would require "up to a week or longer." If designated black-start units were to fail — a real risk, given recent audits showing many unready — the timelines would stretch indefinitely.
In plain speech: in a true national blackout, the nation’s restoration would be a gamble.
V. The Forking Paths Ahead
If all proceeds well, Britain might stumble into light within three days. If the adversities accumulate — cyberattack, internal sabotage, simple human miscalculation — the process would stretch into weeks, even months. In the gravest scenarios, the nation would reconstitute not as one great engine, but as isolated islands of power, each jury-rigged and vulnerable.
Meanwhile, the paradoxical truth is that small and simple systems — the grids of Jersey, Malta, and the like — would outpace their mightier cousins, not despite their modest scale but because of it.
VI. Conclusion
The British grid, in short, is a triumph of late modernity — and like all such triumphs, it carries within itself the seeds of its own fragility. It works magnificently until the day it does not. When that day comes, recovery will be neither swift nor sure, but a slow, halting reweaving of threads too easily frayed.
-
 @ dc814bb0:7a410cb5
2025-04-29 23:07:29
@ dc814bb0:7a410cb5
2025-04-29 23:07:29Hallo welt
[[ ]] Add as many elements as you want? [[X]] The X marks the correct answer! [[ ]] ... this is wrong ... [[X]] ... this has to be selected too ...
-
 @ 975e4ad5:8d4847ce
2025-04-29 08:26:50
@ 975e4ad5:8d4847ce
2025-04-29 08:26:50With the advancement of quantum computers, a new threat emerges for the security of cryptocurrencies and blockchain technologies. These powerful machines have the potential to expose vulnerabilities in traditional cryptographic systems, which could jeopardize the safety of digital wallets. But don’t worry—modern wallets are already equipped to handle this threat with innovative solutions that make your funds nearly impossible to steal, even by a quantum computer. Let’s explore how this works and why you can rest easy.
The Threat of Quantum Computers
To understand how wallets protect us, we first need to grasp what makes quantum computers so dangerous. At the core of most cryptocurrencies, like Bitcoin, lies public and private key cryptography. The public key (or address) is like your bank account number—you share it to receive funds. The private key is like your PIN—it allows you to send funds and must remain secret.
Traditional cryptography, such as the ECDSA algorithm, relies on mathematical problems that are extremely difficult to solve with conventional computers. For instance, deriving a private key from a public key is practically impossible, as it would take millions of years of computation. However, quantum computers, thanks to algorithms like Shor’s, can significantly speed up this process. Theoretically, a sufficiently powerful quantum computer could uncover a private key from a public key in minutes or even seconds.
This is a problem because if someone gains access to your private key, they can send all your funds to their own address. But here’s the good news—modern wallets use a clever solution to render this threat powerless.
How Do Wallets Protect Us?
One of the most effective defenses against quantum computers is the use of one-time addresses in wallets. This means that for every transaction—whether receiving or sending funds—the wallet automatically generates a new public address. The old address, once used, remains in the transaction history but no longer holds any funds, as they are transferred to a new address.
Why Does This Work?
Imagine you’re sending or receiving cryptocurrency. Your wallet creates a new address for that transaction. After the funds are sent or received, that address becomes “used,” and the wallet automatically generates a new one for the next transaction. If a quantum computer manages to derive the private key from the public address of the used address, it will find nothing—because that address is already empty. Your funds are safely transferred to a new address, whose public key has not yet been exposed.
This strategy is known as HD (Hierarchical Deterministic) wallets. It allows the wallet to generate an infinite number of addresses from a single master key (seed) without compromising security. Each new address is unique and cannot be linked to the previous ones, making it impossible to trace your funds, even with a quantum computer.
Automation Makes It Effortless
The best part? You don’t need to worry about this process—it’s fully automated. When you use a modern wallet like MetaMask, Ledger, Trezor, or software wallets for Bitcoin, everything happens behind the scenes. You simply click “receive” or “send,” and the wallet takes care of generating new addresses. There’s no need to understand the complex technical details or manually manage your keys.
For example:
- You want to receive 0.1 BTC. Your wallet provides a new address, which you share with the sender.
- After receiving the funds, the wallet automatically prepares a new address for the next transaction.
- If you send some of the funds, the remaining amount (known as “change”) is sent to another new address generated by the wallet.
This system ensures that public addresses exposed on the blockchain no longer hold funds, making quantum attacks pointless.
Additional Protection: Toward Post-Quantum Cryptography
Beyond one-time addresses, blockchain developers are also working on post-quantum cryptography—algorithms that are resistant to quantum computers. Some blockchain networks are already experimenting with such solutions, like algorithms based on lattices (lattice-based cryptography). These methods don’t rely on the same mathematical problems that quantum computers can solve, offering long-term protection.
In the meantime, one-time addresses combined with current cryptographic standards provide enough security to safeguard your funds until post-quantum solutions become widely adopted.
Why You Shouldn’t Worry
Modern wallets are designed with the future in mind. They not only protect against today’s threats but also anticipate future risks, such as those posed by quantum computers. One-time addresses make exposed public keys useless to hackers, and automation ensures you don’t need to deal with the technicalities. HD wallets, which automatically generate new addresses, make the process seamless and secure for users.
Public key exposure only happens when necessary, reducing the risk of attacks, even from a quantum computer. In conclusion, while quantum computers pose a potential threat, modern wallets already offer effective solutions that make your cryptocurrencies nearly impossible to steal. With one-time addresses and the upcoming adoption of post-quantum cryptography, you can be confident that your funds are safe—today and tomorrow.
-
 @ 7d33ba57:1b82db35
2025-04-29 14:14:11
@ 7d33ba57:1b82db35
2025-04-29 14:14:11Located in eastern Poland, Lublin is a city where history, culture, and youthful energy come together. Often called the "Gateway to the East," Lublin blends Gothic and Renaissance architecture, vibrant street life, and deep historical roots—especially as a center of Jewish heritage and intellectual life.
🏙️ Top Things to See in Lublin
🏰 Lublin Castle
- A striking hilltop castle with a neo-Gothic façade and a beautifully preserved Romanesque chapel (Chapel of the Holy Trinity)
- Don’t miss the frescoes inside—a rare mix of Byzantine and Western art styles
🚪 Old Town (Stare Miasto)
- Wander through cobblestone streets, pastel buildings, and arched gateways
- Filled with cozy cafes, galleries, and vibrant murals
- The Grodzka Gate symbolizes the passage between Christian and Jewish quarters
🕯️ Lublin’s Jewish Heritage
- Visit the Grodzka Gate – NN Theatre, a powerful memorial and museum telling the story of the once-vibrant Jewish community
- Nearby Majdanek Concentration Camp offers a sobering but important historical experience
🎭 Culture & Events
- Lublin is known for its festivals, like Carnaval Sztukmistrzów (Festival of Magicians and Street Performers) and the Night of Culture
- The city has a thriving theatre and music scene, supported by its large student population
🌳 Green Spaces
- Relax in Saski Garden, a peaceful park with walking paths and fountains
- Or take a walk along the Bystrzyca River for a quieter, more local feel
🍽️ Local Tastes
- Sample Polish classics like pierogi, żurek (sour rye soup), and bigos (hunter’s stew)
- Look for modern twists on traditional dishes in Lublin’s growing number of bistros and artisan cafés
🚆 Getting There
- Easy access by train or bus from Warsaw (2–2.5 hours)
- Compact center—easily walkable
-
 @ 957df479:13e9e08e
2025-04-29 20:56:20
@ 957df479:13e9e08e
2025-04-29 20:56:20LiaScript Course
Course Main Title
This is your course initialization stub.
Please see the Docs to find out what is possible in LiaScript.
If you want to use instant help in your Atom IDE, please type lia to see all available shortcuts.
Markdown
You can use common Markdown syntax to create your course, such as:
- Lists
-
ordered or
-
unordered
- ones ...
| Header 1 | Header 2 | | :--------- | :--------- | | Item 1 | Item 2 |
Images:

Extensions
--{{0}}--But you can also include other features such as spoken text.
--{{1}}--Insert any kind of audio file:
{{1}}--{{2}}--Even videos or change the language completely.
{{2-3}}!?video
--{{3 Russian Female}}--Первоначально создан в 2004 году Джоном Грубером (англ. John Gruber) и Аароном Шварцем. Многие идеи языка были позаимствованы из существующих соглашений по разметке текста в электронных письмах...
{{3}}Type "voice" to see a list of all available languages.
Styling
The whole text-block should appear in purple color and with a wobbling effect. Which is a bad example, please use it with caution ... ~~ only this is red ;-) ~~
Charts
Use ASCII-Art to draw diagrams:
Multiline 1.9 | DOTS | *** y | * * - | r r r r r r r*r r r r*r r r r r r r a | * * x | * * i | B B B B B * B B B B B B * B B B B B s | * * | * * * * * * -1 +------------------------------------ 0 x-axis 1Quizzes
A Textquiz
What did the fish say when he hit a concrete wall?
[[dam]]Multiple Choice
Just add as many points as you wish:
[[X]] Only the **X** marks the correct point. [[ ]] Empty ones are wrong. [[X]] ...Single Choice
Just add as many points as you wish:
[( )] ... [(X)] <-- Only the **X** is allowed. [( )] ...Executable Code
A drawing example, for demonstrating that any JavaScript library can be used, also for drawing.
```javascript // Initialize a Line chart in the container with the ID chart1 new Chartist.Line('#chart1', { labels: [1, 2, 3, 4], series: [[100, 120, 180, 200]] });
// Initialize a Line chart in the container with the ID chart2 new Chartist.Bar('#chart2', { labels: [1, 2, 3, 4], series: [[5, 2, 8, 3]] }); ```
Projects
You can make your code executable and define projects:
``` js -EvalScript.js let who = data.first_name + " " + data.last_name;
if(data.online) { who + " is online"; } else { who + " is NOT online"; }
json +Data.json { "first_name" : "Sammy", "last_name" : "Shark", "online" : true } ```More
Find out what you can even do more with quizzes:
https://liascript.github.io/course/?https://raw.githubusercontent.com/liaScript/docs/master/README.md
-
 @ bbb5dda0:f09e2747
2025-04-29 13:46:37
@ bbb5dda0:f09e2747
2025-04-29 13:46:37GitHub Actions (CI/CD) over Nostr
I Spent quite a bit of time on getting Nostr-based GitHub actions working. I have a basic runner implementation now, which i've reworked quite a bit when working with @dan on getting the front-end of it into gitworkshop.dev. We found that the nature of these jobs don't really lend itself to fit within the NIP-90 DVM spec.
What we have now: - A dvm-cicd-runner that - Advertises itself using NIP-89 announcements. - Takes a DVM request with: - repository - branch/ref - path to workflow file (
.yml) - job timeout (max duration) - 🥜 Cashu prepayment for the job timeout (to be refunded) - Pulls the repository and executes the provided workflow file - Sends logs in batches as partial job results - Publishes job results and gets displayed in gitworkshop - Gitworkshop.dev (all nostr:npub15qydau2hjma6ngxkl2cyar74wzyjshvl65za5k5rl69264ar2exs5cyejr work) UI that : - Shows available workflow runners. - Instructing + paying runner to execute workflow file - Displaying job status, live updating with the latest logs / autoscroll, all the stuff you'd expect - Neatly displaying past jobs for the current repositoryTODO'S + Ideas/vision
- TODO: refunding the unused minutes (job timeout - processing time) to the requester
- TODO: create seperate kinds/nip for worflow execution over nostr
- Create separate kinds for streaming arbitrary text data over nostr (line by line logs)
- automated git watchers for projects to kick of jobs
- Separate out workflow management stuff from gitworkshop.dev. A micro-app might serve better to manage runners for git projects etc and takes away pressure from gitworkshop.dev to do it all.
- Perhaps support just running .yaml files, without the requirement to have it in a git repo. Could just be a .yaml file on blossom.
TollGate
I spent most of my time working on TollGate. There's been a lot of back and forth to the drawing board to narrow down what the TollGate protocol looks like. I helped define some concepts on implementing a tollgate which we could use as language to discuss the different components that are part of a tollgate implementation. It helped us narrow down what was implementation and what is part of the protocol.
Current state of the project
- We have a website displaying the project: TollGate.me
- Worked on a basic android app for auto payments, validating we can auto-buy from tollgates by our phones
- Presented TollGate at @Sats 'n Facts
- There's a protocol draft, presented at SEC-04
- We've done workshops, people were able to turn an OpenWRT router into a TollGate
- Building and releasing TollGate as a singular OpenWRT package, installable on any compatible architecture
- Building and releasing TollGate OS v0.0.1 (prebuilt OpenWRT image), targeting a few specific routers
- First tollgate deployed in the wild!! (At a restaurant in Funchal, Madeira)
- Other developers started to make their own adjacent implementations, which decentralizes the protocol already
What's next:
- We're gathering useful real user feedback to be incorporated in OS v0.0.2 soon
- Refine the protocol further
- Showing TollGate at various conferences in Europe throughout the summer
- Keep building the community, it's growing fast
Epoxy (Nostr based Addressing)
Although i've pivoted towards focusing on TollGate I worked out an implementation of my NIP-(1)37 proposal. During SEC-04 I worked out this browser plugin to demonstrate one way to make websites resistant to rugpulls.
It works by looking for a
metatag in the page'shead:html <meta name="nostr-pubkey" relays="relay.site.com,other.relay.com">[hexPubkey]</meta>When we've never recorded a pubkey for this domain, we save it. This pubkey now serves as the owner of the website. It looks for a kind
11111event of that pubkey. It should list the current domain as one of it's domains. If not, it shows a warning.The key concept is that if we visit this website again and one of these scenario's is true: - There is no longer a
metatag - There's another pubkey in themetatag - The pubkey is still on the webpage, but the11111no longer lists this domainThen we consider this domain as RUGPULLED and the user gets an error, suggesting to navigate to other domain listed by this
pubkey. I'd like it to perhaps auto-redirect to another domain listed by the owner, this is especially useful for frequently rugged domains.This extension does try to solve a bootstrapping problem. We need to establish the website's pubkey at some point. We have to start somewhere, which is why the first load is considered as the 'real' one, since we have no way of knowing for sure.
Other
🥜/⚡️ Receipt.Cash - Social Receipt sharing app
During SEC I worked on scratching an itch that has been lingering in my mind since SEC-03 already. And now that vibecoding is a thing it wasn't this huge undertaking anymore to handle the front-end stuff (which i suck at).
The usage scenario is a bunch of bitcoiners that are at a restaurant, we get the bill and want to split it amongst each other. One person can pay the bill, then: - Payer photographs receipt - Payer adds Cashu Payment request - Payer sets dev split % - App turns the receipt + request into a (encrypted) nostr event - The payer shares the event with QR or Share Menu
The friend scan the QR: - Receipt is loaded and displayed - Friend selects items they ordered - Friend hits pay button (⚡️Lightning or 🥜Cashu) and pays - Payment gets sent to Payer's cashu wallet - Dev split set by Payer goes to dev address.
Some features: - Change LLM model that processes the receipt to extract data - Proofs storage + recovery (if anything fails during processing)
Todo's: - Letting payer configure LNURL for payouts - Letting payer edit Receipt before sharing - Fix: live updates on settled items
The repo: receipt-cash
-
 @ a296b972:e5a7a2e8
2025-04-29 07:24:49
@ a296b972:e5a7a2e8
2025-04-29 07:24:4928.04.2025, 16.17 Uhr:
Russische Hobby-Flieger konnten mit ihrem Sportflugzeug namens "Andromeda" unter dem Radar bleiben und haben entlang der Hauptstromtrassen mit einem ukrainischen Zwiebelmesser die Stromleitungen gekappt. In einer scharfen Rechtskurve muss wohl eine Flugzeugtür aufgegangen sein und der Pass des Piloten fiel unbemerkt heraus. Die Identität der Täter konnte so schnell festgestellt werden.
28.04.2025, 16.43 Uhr:
Trump hat das europäische Stromnetz gekauft und die in den Umspannwerken eingebauten US-amerikanischen Chips deaktiviert. Es gibt erst wieder Strom, wenn sich die Koalition der Willigen den Friedensverhandlungen für die Ukraine anschließt. Trump hat bewusst in den sonnenreichen Ländern Spanien und Portugal begonnen, das soll als Warnung für ganz Europa gelten. Frau von der Leyen hat bereits scharfen Protest eingelegt, doch Trump hat die SMS sofort gelöscht.
28.04.2025, 17.12 Uhr:
Selensky hat einen Cyber-Angriff auf das europäische Stromnetz gestartet. Er ist wütend, weil sich Macron in dem 15-Minuten-Gespräch mit Trump am Rande der Beerdigung des Papstes in Rom hat abwimmeln lassen. Er beendet die Strom-Blockade erst, wenn Spanien, Portugal und Frankreich Deutschland dazu zwingen, endlich Taurus zu liefern. Auf die Frage, wie Selensky das angestellt hat, soll er geantwortet haben: "Sie sehen ja, wir können es."
Ist natürlich alles nur Joke! Es sollte nur einmal in Bezug auf die Sprengung der Nordstream 2 Pipelines aufgezeigt werden, wie schnell auch unsereins abstruse Erklärungen liefern kann, die vorne und hinten nicht stimmen können.
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
(Bild von pixabay)
-
 @ 866e0139:6a9334e5
2025-04-29 18:40:31
@ 866e0139:6a9334e5
2025-04-29 18:40:31Autor: Thomas Eisinger. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Vor Kurzem war ich bei einem «Ecstatic Dance» (mehr dazu z. B. hier) dabei. Wer das noch nicht kennt: es lohnt sich! Irgendwann in diesem speziellen Space bekam ich einen Gedanken - oder er kam von irgendwo zu mir: die Vorstellung, dass niemand in meiner Reihe von Eltern, Großeltern, Ahnen je an so etwas hätte teilnehmen können. Einmal, weil es das damals nicht gab. Zum Zweiten, weil ihr Mind niemals für so etwas offen gewesen wäre, gar nicht sein konnte. Sie alle waren einfache Menschen, die genug damit zu tun hatten für das Überleben der eigenen Familie zu sorgen. Urlaub war ein Fremdwort, intellektuelle Faxen gab es ganz sicher keine. Diese meine Vorstellung erschuf ein inneres Bild in mir: ich sah meine beiden Großmütter wild und lebensfroh durch den Raum tanzen! (Übrigens wurden beide 95 Jahre alt, trotz zwei Kriegen, Währungsreform, Hunger und ohne jemals Sport getrieben oder Ernährungsratgeber gelesen zu haben. Dies nur am Rande).
Ich erfreute mich an dem Bild der tanzenden Großmütter, konnte mich eines breiten Grinsens nicht erwehren. Nach dieser Freude wechselte mein Gefühl jäh zu Dankbarkeit. Dafür, in dieser wunderbaren Zeit leben zu dürfen. In der so viel mehr möglich ist als es jemals war. Das enge Korsett, das die Gesellschaft seit Jahrtausenden jedem auferlegt hatte, ist so viel weiter geworden. Nur, wenn man es selbst annehmen möchte (oder zumindest meint, dies tun zu müssen) kann es noch Macht ausüben. Sonst nicht. Die persönliche Freiheit ist größer als jemals zuvor, wenn man sie mit den Hundert Generationen vor uns vergleicht. Natürlich ist aktuell «the Trend not our friend», aber wir haben die Wahl, den Zeitmaßstab selbst anzulegen. 10 Jahre, 100 oder 200 Jahre? Lass es vor Deinem inneren Auge erscheinen ...
Die innere Freiheit ist größer als in all den Zeiten vor meiner Generation (Boomer). Millionen Menschen haben Meditationserfahrung, einige können sich mit Informationsfeldern (jenseits der rechtgläubigen Physik) verbinden und darüber sprechen, ohne dass sie verbrannt werden. Man muss keiner offiziellen Religion mehr folgen, um Verbindung mit dem Höheren zu erlangen. Im Gegenteil, die Ablösung von den Amtskirchen erleichtert dies für viele sogar. Wie auch immer, der eigenen Wahl stehen weder Priester noch Eltern oder starre Konventionen entgegen. Anders als vor 100 oder 200 Jahren. Just do it!
Es geht noch weiter. Wie dankbar bin ich, dass ich in dieser Zeit leben darf. Dass trotz des Leides meiner in ziemlicher Armut lebender Großeltern ihr Wille zum Überleben stärker war: nur deshalb kann ich hier sein. Ich darf all diese Vorzüge genießen, obwohl ich viel weniger hart arbeiten muss(te) als sie. Auch wurde mein Haus nicht ausgebombt und ich musste nie in den Krieg ziehen. Meine beiden Großväter ereilte dieses Schicksal. Ob mein Sohn diesem Schicksal entrinnt?
Wir sollen wieder kriegstüchtig werden. Unfassbar. Doch damit will ich diese Betrachtung nicht enden lassen. Denn nur wenn wir auch begreifen, wie gut es uns allen geht, trotz dieser Regierung, trotz Massenpropaganda, trotz dauernder medialer Panikmache: erst, wenn wir das Leben wirklich lieben, werden wir wissen, wofür es sich wirklich lohnt zu kämpfen. Nicht mit Waffe in der Hand, sondern mit Herz und Verstand.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 83279ad2:bd49240d
2025-04-29 05:53:52
@ 83279ad2:bd49240d
2025-04-29 05:53:52test
-
 @ 4db2f229:205fed9f
2025-04-28 23:25:16
@ 4db2f229:205fed9f
2025-04-28 23:25:16https://www.nexusmods.com/newvegas/mods/80258
If you manage to get it up to date / uncorrupt the data, I give you full liberties to:
- The model itself
- Its XMF and/or XML skeleton
- Patching it to be compatible with any other gun mods
- other fixes
- and full credit handed over to you
I think this has honestly been abandoned by it's original developer, and since I am just hanging onto the file? I decided it'd be better maintained in someone elses hands, and with community much more responsible than Nexus. Honestly if I did not archive this mod? It would of been vaporware.
But in it's current state it's not fit for being playable. I did manage to save media of when it was playable however.
-
 @ c3b2802b:4850599c
2025-04-29 13:24:06
@ c3b2802b:4850599c
2025-04-29 13:24:06Am 11. April 2022, einem sonnigen Frühlingstag, schaute ich gegen 11 Uhr seit langem wieder einmal bei Roßleben an der Unstrut mit Muße in den Himmel. Gemeinsam mit Regina, meiner Frau. Wir sind jetzt im Ruhestand – und hatten uns im Jahr 1974 unter dem Himmel von Roßleben verliebt.
Was wir da sahen, können Sie im Titelbild oben nachvollziehen. Überrascht beobachteten wir ein Weile, was da passiert, doch die Streifen, offenkundig von Flugzeugen hinterlassen, lösten sich nicht auf, sondern verbanden sich allmählich zu einem zusammenhängenden Dunstschleier, festgehalten im folgenden Foto:

Überrascht waren wir, weil wir vor knapp 50 Jahren am gleichen Himmel zwar auch schon Flugzeuge gesehen hatten, die hatten allerdings nicht derartige von Horizont zu Horizont reichenden Spuren hinterlassen. Einige Tage später gelang mir eine Aufnahme, die einen von anno dazumal vertrauten Kondensstreifen eines Flugzeuges zeigt:

Gemeint ist die senkrecht in der Bildmitte verlaufende kurze Spur. Darunter der waagrechte Streifen zeigt das heute eher übliche Bild.
Als neugieriger Mensch bat ich das für solche Fragen zuständige Bundesumweltamt um Auskunft, wie diese Himmelserscheinungen zu erklären sind. Hier die Fragen, die ich mit den Fotos an das Umweltbundesamt gesendet habe:
1. Seit wann genau hinterlassen Flugzeuge über deutschem Luftraum Spuren, welche länger als 5 Minuten am Himmel sichtbar sind, sich ausbreiten und in Form von Dunstschleiern über Stunden am Himmel verbleiben?
2. Inwieweit wurde die Durchführung entsprechender Beschlüsse, welche die beobachtbare Schleierbildung herbeiführen, von demokratischen Gremien unseres Landes, z.B. dem deutschen Bundestag, genehmigt?
3. Welche Entscheidungsträger in unserem Land sind für diese Vorgänge verantwortlich?
4. Gibt es in diesem Zusammenhang internationale Geoingeneering-Programme, an denen Deutschland beteiligt ist? Wenn ja, welche sind das?
5. Was ist Ihnen über Partikel bzw. Substanzen bekannt, welche die langandauernde Sichtbarkeit dieser Schleier verursachen?
6. Was ist Ihnen über Folgeschäden durch die offenkundige Beeinflussung der Lichteinstrahlung oder durch Herabsenken von Partikeln bzw. Substanzen in diesen Schleiern auf Pflanzen, Tiere und Menschen bekannt?
7. Welche Möglichkeiten sehen Sie in Ihrem Amt, zur wissenschaftlichen Aufklärung und ggf. Beendigung dieser Dunstschleier-Aktivitäten beizutragen?
Hier die Antwort des Bundesamtes:
Sehr geehrter Herr Professor, danke für Ihre Anfrage.
Aus unserer Sicht handelt es sich bei Ihren Beobachtungen um Kondensstreifen. Sie entstehen in hinreichend kalter Atmosphäre als Folge der Wasserdampfemissionen aus Flugzeugtriebwerken. Bei niedriger Feuchte lösen sich Kondensstreifen rasch wieder auf. Ist die Atmosphäre jedoch hinreichend feucht, können Kondensstreifen länger existieren und weiter wachsen. Unter geeigneten Bedingungen können sie sich zu großflächigen Zirruswolken, die im Falle einer solchen Entstehungsgeschichte Contrail-Cirrus heißen, entwickeln. Contrail-Cirrus ist dann nicht mehr von natürlichen Zirren unterscheidbar, falls nicht seine gesamte Entstehungsgeschichte beobachtet wurde.
Nehmen Zirruswolken, die optisch sehr dünn sein können, eine große Fläche ein, erscheint dem Beobachter der Himmel milchig weiß. Im Mittel sind rund 0,06 Prozent der Erde mit (linienförmigen) Kondensstreifen bedeckt. Gegenden mit hohem Flugverkehrsaufkommen erreichen deutlich höhere Bedeckungsgrade. So lag Mitte der neunziger Jahre der Wert für Europa bei 0,5 Prozent. Der Bedeckungsgrad durch Contrail-Cirrus ist noch nicht bekannt. Erste Schätzungen liefern Werte, die etwa zehnmal so groß sind wie der Bedeckungsgrad mit linienförmigen Kondensstreifen.
Altern Kondensstreifen, bleiben sie nicht glatt, sondern können Formen bilden. Dieser Vorgang ist ein lange bekanntes Phänomen und eine Folge der Turbulenz, die in der Atmosphäre allgegenwärtig ist. Diese Formen lassen sich auch durch Modellsimulationen reproduzieren.
Mehrere Kondensstreifen nebeneinander entstehen zum Beispiel dadurch, dass Flugzeuge festen Routen folgen und die Windrichtung in der Höhe von der Flugroute abweicht. Die Kondensstreifen verschieben sich dadurch seitlich. An Knotenpunkten der Flugrouten können sich Kondensstreifen unterschiedlicher Orientierung bilden. Als Folge der Verschiebung der Kondensstreifen können dann auch rautenförmige Muster entstehen. Da Windrichtung und -geschwindigkeit praktisch nie gleich sind, entstehen aus vormals geraden Mustern gekrümmte Formen. Außerdem fliegen Flugzeuge nicht immer nur geradeaus, sondern auch Kurven, insbesondere während Warteschleifen in Flughafennähe. In diesem Fall können gekrümmte Kondensstreifen entstehen.
Nähere Informationen zur Bildung von Kondensstreifen gibt das DLR auf folgender Internetseite: http://www.dlr.de/pa/desktopdefault.aspx/tabid-2554/3836_read-5746/
Uns sind die Vorschläge, die unter dem Stichwort Geo-Engineering oder Climate-Engineering zusammengefasst werden, bekannt. Wir haben dazu bereits 2011 eine umfassende Broschüre veröffentlicht.
In dieser Broschüre stellen wir auch die großen Risiken, die mit Geo-Engineering verbunden wären, ausführlich dar. Es gibt in Deutschland auch keinerlei Planungen staatlicher Institutionen zur Durchführung von Geo-Engineering. Die existierenden Vorschläge zum Geo-Engineering sind zum größten Teil nicht ausgereift und werden auch in der Praxis nicht angewendet. Es ist nicht geklärt, welche schwerwiegenden, unerwünschten Nebenwirkungen auftreten könnten. Zudem gibt es gar keine ausreichende rechtliche Basis für Geo-Engineering. Wörtlich heißt es in unserer Broschüre auf Seite 4: „Angesichts der Tragweite von Geo-Engineering-Maßnahmen und den großen Unsicherheiten bei der Abschätzung von Folgen im komplexen Erdsystem rät das UBA aus Vorsorgegründen zu größter Zurückhaltung und bis zu einer deutlichen Verbesserung des Wissens um die Interdependenzen zwischen Geoprozessen zu einem Moratorium für den Einsatz solcher Maßnahmen.“ (https://www.umweltbundesamt.de/publikationen/geo-engineering-wirksamer-klimaschutz-groessenwahn)
Wir hoffen, die Informationen helfen Ihnen weiter. Mit freundlichen Grüßen Im Auftrag
Team Bürgerservice, Umweltbundesamt, Postfach 14 06, 06813 Dessau-Roßlau
Da ich kein Wolken-Forscher werden mag, überlasse ich Ihnen gern das Urteil über meine Fragen und die Passung der Antworten seitens unserer Regierungsbehörde.
Spannend ist heute, drei Jahre nach diesem kleinen Briefwechsel (erstmals veröffentlicht im April 2022 auf der Plattform der Zukunftskommunen), dass vom Senat des US Bundesstaates Florida am 3. April 2025 ein Gesetz verabschiedet wurde, welches das Versprühen von Chemikalien durch Flugzeuge unter Strafe stellt. Hier ein kurzer Auszug:
Verbot von Geoengineering und wetterverändernden Aktivitäten
(1) Die Injektion, Freisetzung oder Dispersion von Chemikalien, chemischen Verbindungen, Substanzen in die Atmosphäre innerhalb der Grenzen dieses Staates zu dem Zweck der Beeinflussung von Temperatur, Wetter, Klima oder um die Intensität des Sonnenlichts zu beeinflussen, ist verboten.
(2) Jede Person, jede öffentliche oder private Körperschaft, die eine Geo-Engineering-Aktion oder Wetterbeeinflussung unter Verstoß gegen dieses Verbot durchführt, macht sich schuldig eines Verbrechens dritten und zweiten Grades, auf das eine Geldstrafe von bis zu 100.000 Dollar fällig wird. ... Luftfahrzeugbetreiber oder Fluglotsen, die ein Verbrechen dritten Grades dieser Art begehen, werden bestraft mit einer Geldstrafe von bis zu $5.000 und bis zu 5 Jahren Gefängnis.
Den kompletten Text können Sie hier nachlesen. In Tennessee sowie in über 20 weiteren US Bundesstaaten sind ähnliche Gesetze auf dem Weg. Jetzt dürfen wir neugierig sein, wie die Rotkäppchen - Story in anderen Ländern, z.B. in Deutschland weitergeht.
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ 88cc134b:5ae99079
2025-04-29 11:39:51
@ 88cc134b:5ae99079
2025-04-29 11:39:51one, two, three, four, five, six
-
 @ 4ba8e86d:89d32de4
2025-04-28 22:39:20
@ 4ba8e86d:89d32de4
2025-04-28 22:39:20Como funciona o PGP.
O texto a seguir foi retirado do capítulo 1 do documento Introdução à criptografia na documentação do PGP 6.5.1. Copyright © 1990-1999 Network Associates, Inc. Todos os direitos reservados.
-O que é criptografia? -Criptografia forte -Como funciona a criptografia? -Criptografia convencional -Cifra de César -Gerenciamento de chaves e criptografia convencional -Criptografia de chave pública -Como funciona o PGP - Chaves • Assinaturas digitais -Funções hash • Certificados digitais -Distribuição de certificados -Formatos de certificado •Validade e confiança -Verificando validade -Estabelecendo confiança -Modelos de confiança • Revogação de certificado -Comunicar que um certificado foi revogado -O que é uma senha? -Divisão de chave
Os princípios básicos da criptografia.
Quando Júlio César enviou mensagens aos seus generais, ele não confiou nos seus mensageiros. Então ele substituiu cada A em suas mensagens por um D, cada B por um E, e assim por diante através do alfabeto. Somente alguém que conhecesse a regra “shift by 3” poderia decifrar suas mensagens. E assim começamos.
Criptografia e descriptografia.
Os dados que podem ser lidos e compreendidos sem quaisquer medidas especiais são chamados de texto simples ou texto não criptografado. O método de disfarçar o texto simples de forma a ocultar sua substância é chamado de criptografia. Criptografar texto simples resulta em um jargão ilegível chamado texto cifrado. Você usa criptografia para garantir que as informações sejam ocultadas de qualquer pessoa a quem não se destinam, mesmo daqueles que podem ver os dados criptografados. O processo de reverter o texto cifrado ao texto simples original é chamado de descriptografia . A Figura 1-1 ilustra esse processo.
https://image.nostr.build/0e2fcb71ed86a6083e083abbb683f8c103f44a6c6db1aeb2df10ae51ec97ebe5.jpg
Figura 1-1. Criptografia e descriptografia
O que é criptografia?
Criptografia é a ciência que usa a matemática para criptografar e descriptografar dados. A criptografia permite armazenar informações confidenciais ou transmiti-las através de redes inseguras (como a Internet) para que não possam ser lidas por ninguém, exceto pelo destinatário pretendido. Embora a criptografia seja a ciência que protege os dados, a criptoanálise é a ciência que analisa e quebra a comunicação segura. A criptoanálise clássica envolve uma combinação interessante de raciocínio analítico, aplicação de ferramentas matemáticas, descoberta de padrões, paciência, determinação e sorte. Os criptoanalistas também são chamados de atacantes. A criptologia abrange tanto a criptografia quanto a criptoanálise.
Criptografia forte.
"Existem dois tipos de criptografia neste mundo: a criptografia que impedirá a sua irmã mais nova de ler os seus arquivos, e a criptografia que impedirá os principais governos de lerem os seus arquivos. Este livro é sobre o último." --Bruce Schneier, Criptografia Aplicada: Protocolos, Algoritmos e Código Fonte em C. PGP também trata deste último tipo de criptografia. A criptografia pode ser forte ou fraca, conforme explicado acima. A força criptográfica é medida no tempo e nos recursos necessários para recuperar o texto simples. O resultado de uma criptografia forte é um texto cifrado que é muito difícil de decifrar sem a posse da ferramenta de decodificação apropriada. Quão díficil? Dado todo o poder computacional e o tempo disponível de hoje – mesmo um bilhão de computadores fazendo um bilhão de verificações por segundo – não é possível decifrar o resultado de uma criptografia forte antes do fim do universo. Alguém poderia pensar, então, que uma criptografia forte resistiria muito bem até mesmo contra um criptoanalista extremamente determinado. Quem pode realmente dizer? Ninguém provou que a criptografia mais forte disponível hoje resistirá ao poder computacional de amanhã. No entanto, a criptografia forte empregada pelo PGP é a melhor disponível atualmente.
Contudo, a vigilância e o conservadorismo irão protegê-lo melhor do que as alegações de impenetrabilidade.
Como funciona a criptografia?
Um algoritmo criptográfico, ou cifra, é uma função matemática usada no processo de criptografia e descriptografia. Um algoritmo criptográfico funciona em combinação com uma chave – uma palavra, número ou frase – para criptografar o texto simples. O mesmo texto simples é criptografado em texto cifrado diferente com chaves diferentes. A segurança dos dados criptografados depende inteiramente de duas coisas: a força do algoritmo criptográfico e o sigilo da chave. Um algoritmo criptográfico, mais todas as chaves possíveis e todos os protocolos que o fazem funcionar constituem um criptossistema. PGP é um criptossistema.
Criptografia convencional.
Na criptografia convencional, também chamada de criptografia de chave secreta ou de chave simétrica , uma chave é usada tanto para criptografia quanto para descriptografia. O Data Encryption Standard (DES) é um exemplo de criptossistema convencional amplamente empregado pelo Governo Federal. A Figura 1-2 é uma ilustração do processo de criptografia convencional. https://image.nostr.build/328b73ebaff84c949df2560bbbcec4bc3b5e3a5163d5fbb2ec7c7c60488f894c.jpg
Figura 1-2. Criptografia convencional
Cifra de César.
Um exemplo extremamente simples de criptografia convencional é uma cifra de substituição. Uma cifra de substituição substitui uma informação por outra. Isso é feito com mais frequência compensando as letras do alfabeto. Dois exemplos são o Anel Decodificador Secreto do Capitão Meia-Noite, que você pode ter possuído quando era criança, e a cifra de Júlio César. Em ambos os casos, o algoritmo serve para compensar o alfabeto e a chave é o número de caracteres para compensá-lo. Por exemplo, se codificarmos a palavra "SEGREDO" usando o valor chave de César de 3, deslocaremos o alfabeto para que a terceira letra abaixo (D) comece o alfabeto. Então começando com A B C D E F G H I J K L M N O P Q R S T U V W X Y Z e deslizando tudo para cima em 3, você obtém DEFGHIJKLMNOPQRSTUVWXYZABC onde D=A, E=B, F=C e assim por diante. Usando este esquema, o texto simples, "SECRET" é criptografado como "VHFUHW". Para permitir que outra pessoa leia o texto cifrado, você diz a ela que a chave é 3. Obviamente, esta é uma criptografia extremamente fraca para os padrões atuais, mas, ei, funcionou para César e ilustra como funciona a criptografia convencional.
Gerenciamento de chaves e criptografia convencional.
A criptografia convencional tem benefícios. É muito rápido. É especialmente útil para criptografar dados que não vão a lugar nenhum. No entanto, a criptografia convencional por si só como meio de transmissão segura de dados pode ser bastante cara, simplesmente devido à dificuldade de distribuição segura de chaves. Lembre-se de um personagem do seu filme de espionagem favorito: a pessoa com uma pasta trancada e algemada ao pulso. Afinal, o que há na pasta? Provavelmente não é o código de lançamento de mísseis/fórmula de biotoxina/plano de invasão em si. É a chave que irá descriptografar os dados secretos. Para que um remetente e um destinatário se comuniquem com segurança usando criptografia convencional, eles devem chegar a um acordo sobre uma chave e mantê-la secreta entre si. Se estiverem em locais físicos diferentes, devem confiar em um mensageiro, no Bat Phone ou em algum outro meio de comunicação seguro para evitar a divulgação da chave secreta durante a transmissão. Qualquer pessoa que ouvir ou interceptar a chave em trânsito poderá posteriormente ler, modificar e falsificar todas as informações criptografadas ou autenticadas com essa chave. Do DES ao Anel Decodificador Secreto do Capitão Midnight, o problema persistente com a criptografia convencional é a distribuição de chaves: como você leva a chave ao destinatário sem que alguém a intercepte?
Criptografia de chave pública.
Os problemas de distribuição de chaves são resolvidos pela criptografia de chave pública, cujo conceito foi introduzido por Whitfield Diffie e Martin Hellman em 1975. (Há agora evidências de que o Serviço Secreto Britânico a inventou alguns anos antes de Diffie e Hellman, mas a manteve um segredo militar - e não fez nada com isso.
[JH Ellis: The Possibility of Secure Non-Secret Digital Encryption, CESG Report, January 1970]) A criptografia de chave pública é um esquema assimétrico que usa um par de chaves para criptografia: uma chave pública, que criptografa os dados, e uma chave privada ou secreta correspondente para descriptografia. Você publica sua chave pública para o mundo enquanto mantém sua chave privada em segredo. Qualquer pessoa com uma cópia da sua chave pública pode criptografar informações que somente você pode ler. Até mesmo pessoas que você nunca conheceu. É computacionalmente inviável deduzir a chave privada da chave pública. Qualquer pessoa que possua uma chave pública pode criptografar informações, mas não pode descriptografá-las. Somente a pessoa que possui a chave privada correspondente pode descriptografar as informações. https://image.nostr.build/fdb71ae7a4450a523456827bdd509b31f0250f63152cc6f4ba78df290887318b.jpg
Figura 1-3. Criptografia de chave pública O principal benefício da criptografia de chave pública é que ela permite que pessoas que não possuem nenhum acordo de segurança pré-existente troquem mensagens com segurança. A necessidade de remetente e destinatário compartilharem chaves secretas através de algum canal seguro é eliminada; todas as comunicações envolvem apenas chaves públicas e nenhuma chave privada é transmitida ou compartilhada. Alguns exemplos de criptossistemas de chave pública são Elgamal (nomeado em homenagem a seu inventor, Taher Elgamal), RSA (nomeado em homenagem a seus inventores, Ron Rivest, Adi Shamir e Leonard Adleman), Diffie-Hellman (nomeado, você adivinhou, em homenagem a seus inventores). ) e DSA, o algoritmo de assinatura digital (inventado por David Kravitz). Como a criptografia convencional já foi o único meio disponível para transmitir informações secretas, o custo dos canais seguros e da distribuição de chaves relegou a sua utilização apenas àqueles que podiam pagar, como governos e grandes bancos (ou crianças pequenas com anéis descodificadores secretos). A criptografia de chave pública é a revolução tecnológica que fornece criptografia forte para as massas adultas. Lembra do mensageiro com a pasta trancada e algemada ao pulso? A criptografia de chave pública o tira do mercado (provavelmente para seu alívio).
Como funciona o PGP.
O PGP combina alguns dos melhores recursos da criptografia convencional e de chave pública. PGP é um criptossistema híbrido. Quando um usuário criptografa texto simples com PGP, o PGP primeiro compacta o texto simples. A compactação de dados economiza tempo de transmissão do modem e espaço em disco e, mais importante ainda, fortalece a segurança criptográfica. A maioria das técnicas de criptoanálise explora padrões encontrados no texto simples para quebrar a cifra. A compressão reduz esses padrões no texto simples, aumentando assim enormemente a resistência à criptoanálise. (Arquivos que são muito curtos para compactar ou que não são compactados bem não são compactados.) O PGP então cria uma chave de sessão, que é uma chave secreta única. Esta chave é um número aleatório gerado a partir dos movimentos aleatórios do mouse e das teclas digitadas. Esta chave de sessão funciona com um algoritmo de criptografia convencional rápido e muito seguro para criptografar o texto simples; o resultado é texto cifrado. Depois que os dados são criptografados, a chave da sessão é criptografada na chave pública do destinatário. Essa chave de sessão criptografada com chave pública é transmitida junto com o texto cifrado ao destinatário.
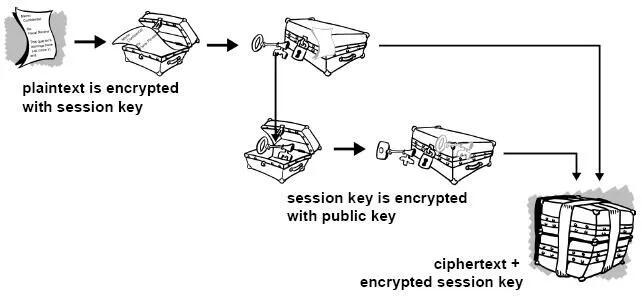
Figura 1-4. Como funciona a criptografia PGP A descriptografia funciona ao contrário. A cópia do PGP do destinatário usa sua chave privada para recuperar a chave de sessão temporária, que o PGP usa para descriptografar o texto cifrado criptografado convencionalmente.

Figura 1-5. Como funciona a descriptografia PGP A combinação dos dois métodos de criptografia combina a conveniência da criptografia de chave pública com a velocidade da criptografia convencional. A criptografia convencional é cerca de 1.000 vezes mais rápida que a criptografia de chave pública. A criptografia de chave pública, por sua vez, fornece uma solução para
problemas de distribuição de chaves e transmissão de dados. Usados em conjunto, o desempenho e a distribuição de chaves são melhorados sem qualquer sacrifício na segurança.
Chaves.
Uma chave é um valor que funciona com um algoritmo criptográfico para produzir um texto cifrado específico. As chaves são basicamente números muito, muito, muito grandes. O tamanho da chave é medido em bits; o número que representa uma chave de 1024 bits é enorme. Na criptografia de chave pública, quanto maior a chave, mais seguro é o texto cifrado. No entanto, o tamanho da chave pública e o tamanho da chave secreta da criptografia convencional não têm nenhuma relação. Uma chave convencional de 80 bits tem a força equivalente a uma chave pública de 1.024 bits. Uma chave convencional de 128 bits é equivalente a uma chave pública de 3.000 bits. Novamente, quanto maior a chave, mais segura, mas os algoritmos usados para cada tipo de criptografia são muito diferentes e, portanto, a comparação é como a de maçãs com laranjas. Embora as chaves pública e privada estejam matematicamente relacionadas, é muito difícil derivar a chave privada dada apenas a chave pública; no entanto, derivar a chave privada é sempre possível, desde que haja tempo e capacidade computacional suficientes. Isto torna muito importante escolher chaves do tamanho certo; grande o suficiente para ser seguro, mas pequeno o suficiente para ser aplicado rapidamente. Além disso, você precisa considerar quem pode estar tentando ler seus arquivos, quão determinados eles estão, quanto tempo têm e quais podem ser seus recursos. Chaves maiores serão criptograficamente seguras por um longo período de tempo. Se o que você deseja criptografar precisar ficar oculto por muitos anos, você pode usar uma chave muito grande. Claro, quem sabe quanto tempo levará para determinar sua chave usando os computadores mais rápidos e eficientes de amanhã? Houve um tempo em que uma chave simétrica de 56 bits era considerada extremamente segura. As chaves são armazenadas de forma criptografada. O PGP armazena as chaves em dois arquivos no seu disco rígido; um para chaves públicas e outro para chaves privadas. Esses arquivos são chamados de chaveiros. Ao usar o PGP, você normalmente adicionará as chaves públicas dos seus destinatários ao seu chaveiro público. Suas chaves privadas são armazenadas em seu chaveiro privado. Se você perder seu chaveiro privado, não será possível descriptografar nenhuma informação criptografada nas chaves desse anel.
Assinaturas digitais.
Um grande benefício da criptografia de chave pública é que ela fornece um método para empregar assinaturas digitais. As assinaturas digitais permitem ao destinatário da informação verificar a autenticidade da origem da informação e também verificar se a informação está intacta. Assim, as assinaturas digitais de chave pública fornecem autenticação e integridade de dados. A assinatura digital também proporciona o não repúdio, o que significa que evita que o remetente alegue que não enviou realmente as informações. Esses recursos são tão fundamentais para a criptografia quanto a privacidade, se não mais. Uma assinatura digital tem a mesma finalidade de uma assinatura manuscrita. No entanto, uma assinatura manuscrita é fácil de falsificar. Uma assinatura digital é superior a uma assinatura manuscrita porque é quase impossível de ser falsificada, além de atestar o conteúdo da informação, bem como a identidade do signatário.
Algumas pessoas tendem a usar mais assinaturas do que criptografia. Por exemplo, você pode não se importar se alguém souber que você acabou de depositar US$ 1.000 em sua conta, mas quer ter certeza de que foi o caixa do banco com quem você estava lidando. A maneira básica pela qual as assinaturas digitais são criadas é ilustrada na Figura 1-6 . Em vez de criptografar informações usando a chave pública de outra pessoa, você as criptografa com sua chave privada. Se as informações puderem ser descriptografadas com sua chave pública, elas deverão ter se originado em você.
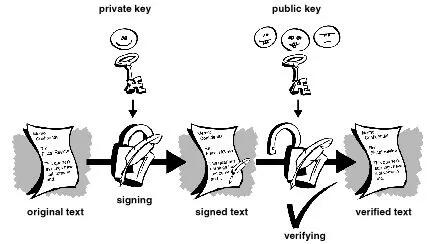
Figura 1-6. Assinaturas digitais simples
Funções hash.
O sistema descrito acima apresenta alguns problemas. É lento e produz um enorme volume de dados – pelo menos o dobro do tamanho da informação original. Uma melhoria no esquema acima é a adição de uma função hash unidirecional no processo. Uma função hash unidirecional recebe uma entrada de comprimento variável – neste caso, uma mensagem de qualquer comprimento, até mesmo milhares ou milhões de bits – e produz uma saída de comprimento fixo; digamos, 160 bits. A função hash garante que, se a informação for alterada de alguma forma – mesmo que por apenas um bit – seja produzido um valor de saída totalmente diferente. O PGP usa uma função hash criptograficamente forte no texto simples que o usuário está assinando. Isso gera um item de dados de comprimento fixo conhecido como resumo da mensagem. (Novamente, qualquer alteração nas informações resulta em um resumo totalmente diferente.) Então o PGP usa o resumo e a chave privada para criar a “assinatura”. O PGP transmite a assinatura e o texto simples juntos. Ao receber a mensagem, o destinatário utiliza o PGP para recalcular o resumo, verificando assim a assinatura. O PGP pode criptografar o texto simples ou não; assinar texto simples é útil se alguns dos destinatários não estiverem interessados ou não forem capazes de verificar a assinatura. Desde que uma função hash segura seja usada, não há como retirar a assinatura de alguém de um documento e anexá-la a outro, ou alterar uma mensagem assinada de qualquer forma. A menor alteração em um documento assinado causará falha no processo de verificação da assinatura digital.
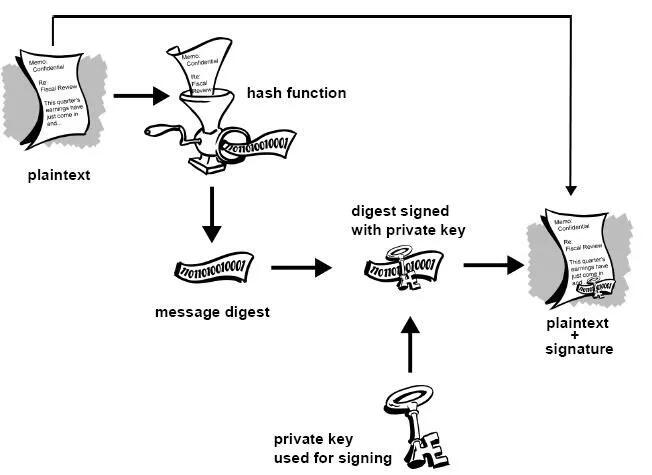
Figura 1-7. Assinaturas digitais seguras As assinaturas digitais desempenham um papel importante na autenticação e validação de chaves de outros usuários PGP.
Certificados digitais.
Um problema com os criptosistemas de chave pública é que os usuários devem estar constantemente vigilantes para garantir que estão criptografando com a chave da pessoa correta. Num ambiente onde é seguro trocar chaves livremente através de servidores públicos, os ataques man-in-the-middle são uma ameaça potencial. Neste tipo de ataque, alguém publica uma chave falsa com o nome e ID de usuário do destinatário pretendido. Os dados criptografados – e interceptados por – o verdadeiro proprietário desta chave falsa estão agora em mãos erradas. Em um ambiente de chave pública, é vital que você tenha certeza de que a chave pública para a qual você está criptografando os dados é de fato a chave pública do destinatário pretendido e não uma falsificação. Você pode simplesmente criptografar apenas as chaves que foram entregues fisicamente a você. Mas suponha que você precise trocar informações com pessoas que nunca conheceu; como você pode saber se tem a chave correta? Os certificados digitais, ou certs, simplificam a tarefa de estabelecer se uma chave pública realmente pertence ao suposto proprietário. Um certificado é uma forma de credencial. Exemplos podem ser sua carteira de motorista, seu cartão de previdência social ou sua certidão de nascimento. Cada um deles contém algumas informações que identificam você e alguma autorização informando que outra pessoa confirmou sua identidade. Alguns certificados, como o seu passaporte, são uma confirmação importante o suficiente da sua identidade para que você não queira perdê-los, para que ninguém os use para se passar por você.
Um certificado digital são dados que funcionam como um certificado físico. Um certificado digital é uma informação incluída na chave pública de uma pessoa que ajuda outras pessoas a verificar se uma chave é genuína ou válida. Os certificados digitais são usados para impedir tentativas de substituir a chave de uma pessoa por outra.
Um certificado digital consiste em três coisas:
● Uma chave pública.
● Informações do certificado. (Informações de "identidade" sobre o usuário, como nome, ID do usuário e assim por diante.) ● Uma ou mais assinaturas digitais.
O objetivo da assinatura digital em um certificado é afirmar que as informações do certificado foram atestadas por alguma outra pessoa ou entidade. A assinatura digital não atesta a autenticidade do certificado como um todo; ele atesta apenas que as informações de identidade assinadas acompanham ou estão vinculadas à chave pública. Assim, um certificado é basicamente uma chave pública com uma ou duas formas de identificação anexadas, além de um forte selo de aprovação de algum outro indivíduo confiável.
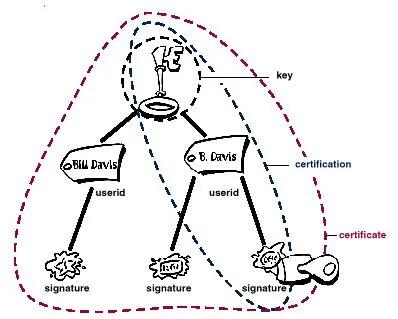 Figura 1-8. Anatomia de um certificado PGP
Figura 1-8. Anatomia de um certificado PGPDistribuição de certificados.
Os certificados são utilizados quando é necessário trocar chaves públicas com outra pessoa. Para pequenos grupos de pessoas que desejam se comunicar com segurança, é fácil trocar manualmente disquetes ou e-mails contendo a chave pública de cada proprietário. Esta é a distribuição manual de chave pública e é prática apenas até certo ponto. Além desse ponto, é necessário implementar sistemas que possam fornecer os mecanismos necessários de segurança, armazenamento e troca para que colegas de trabalho, parceiros de negócios ou estranhos possam se comunicar, se necessário. Eles podem vir na forma de repositórios somente de armazenamento, chamados Servidores de Certificados, ou sistemas mais estruturados que fornecem recursos adicionais de gerenciamento de chaves e são chamados de Infraestruturas de Chave Pública (PKIs).
Servidores de certificados.
Um servidor de certificados, também chamado de servidor certificado ou servidor de chaves, é um banco de dados que permite aos usuários enviar e recuperar certificados digitais. Um servidor certificado geralmente fornece alguns recursos administrativos que permitem que uma empresa mantenha suas políticas de segurança – por exemplo, permitindo que apenas as chaves que atendam a determinados requisitos sejam armazenadas.
Infraestruturas de Chave Pública.
Uma PKI contém os recursos de armazenamento de certificados de um servidor de certificados, mas também fornece recursos de gerenciamento de certificados (a capacidade de emitir, revogar, armazenar, recuperar e confiar em certificados). A principal característica de uma PKI é a introdução do que é conhecido como Autoridade Certificadora,ou CA, que é uma entidade humana — uma pessoa, grupo, departamento, empresa ou outra associação — que uma organização autorizou a emitir certificados para seus usuários de computador. (A função de uma CA é análoga à do Passport Office do governo de um país.) Uma CA cria certificados e os assina digitalmente usando a chave privada da CA. Devido ao seu papel na criação de certificados, a CA é o componente central de uma PKI. Usando a chave pública da CA, qualquer pessoa que queira verificar a autenticidade de um certificado verifica a assinatura digital da CA emissora e, portanto, a integridade do conteúdo do certificado (mais importante ainda, a chave pública e a identidade do titular do certificado).
Formatos de certificado.
Um certificado digital é basicamente uma coleção de informações de identificação vinculadas a uma chave pública e assinadas por um terceiro confiável para provar sua autenticidade. Um certificado digital pode ter vários formatos diferentes.
O PGP reconhece dois formatos de certificado diferentes:
● Certificados PGP ● Certificados X.509 Formato do certificado PGP. Um certificado PGP inclui (mas não está limitado a) as seguintes informações: ● O número da versão do PGP — identifica qual versão do PGP foi usada para criar a chave associada ao certificado. A chave pública do titular do certificado — a parte pública do seu par de chaves, juntamente com o algoritmo da chave: RSA, DH (Diffie-Hellman) ou DSA (Algoritmo de Assinatura Digital).
● As informações do detentor do certificado — consistem em informações de “identidade” sobre o usuário, como seu nome, ID de usuário, fotografia e assim por diante. ● A assinatura digital do proprietário do certificado — também chamada de autoassinatura, é a assinatura que utiliza a chave privada correspondente da chave pública associada ao certificado. ● O período de validade do certificado — a data/hora de início e a data/hora de expiração do certificado; indica quando o certificado irá expirar. ● O algoritmo de criptografia simétrica preferido para a chave — indica o algoritmo de criptografia para o qual o proprietário do certificado prefere que as informações sejam criptografadas. Os algoritmos suportados são CAST, IDEA ou Triple-DES. Você pode pensar em um certificado PGP como uma chave pública com um ou mais rótulos vinculados a ele (veja a Figura 1.9 ). Nessas 'etiquetas' você encontrará informações que identificam o proprietário da chave e uma assinatura do proprietário da chave, que afirma que a chave e a identificação andam juntas. (Essa assinatura específica é chamada de autoassinatura; todo certificado PGP contém uma autoassinatura.) Um aspecto único do formato de certificado PGP é que um único certificado pode conter múltiplas assinaturas. Várias ou muitas pessoas podem assinar o par chave/identificação para atestar a sua própria garantia de que a chave pública pertence definitivamente ao proprietário especificado. Se você procurar em um servidor de certificados público, poderá notar que certos certificados, como o do criador do PGP, Phil Zimmermann, contêm muitas assinaturas. Alguns certificados PGP consistem em uma chave pública com vários rótulos, cada um contendo um meio diferente de identificar o proprietário da chave (por exemplo, o nome do proprietário e a conta de e-mail corporativa, o apelido do proprietário e a conta de e-mail residencial, uma fotografia do proprietário — tudo em um certificado). A lista de assinaturas de cada uma dessas identidades pode ser diferente; as assinaturas atestam a autenticidade de que um dos rótulos pertence à chave pública, e não que todos os rótulos da chave sejam autênticos. (Observe que 'autêntico' está nos olhos de quem vê - assinaturas são opiniões, e diferentes pessoas dedicam diferentes níveis de devida diligência na verificação da autenticidade antes de assinar uma chave.)
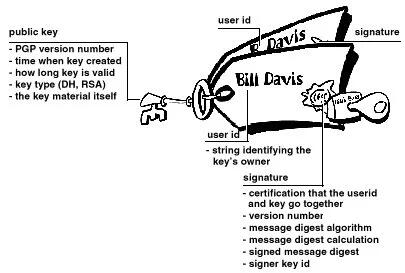 Figura 1-9. Um certificado PGP
Figura 1-9. Um certificado PGPFormato de certificado X.509.
X.509 é outro formato de certificado muito comum. Todos os certificados X.509 estão em conformidade com o padrão internacional ITU-T X.509; assim (teoricamente) os certificados X.509 criados para um aplicativo podem ser usados por qualquer aplicativo compatível com X.509. Na prática, porém, diferentes empresas criaram suas próprias extensões para certificados X.509, e nem todas funcionam juntas. Um certificado exige que alguém valide que uma chave pública e o nome do proprietário da chave andam juntos. Com os certificados PGP, qualquer pessoa pode desempenhar o papel de validador. Com certificados X.509, o validador é sempre uma Autoridade Certificadora ou alguém designado por uma CA. (Tenha em mente que os certificados PGP também suportam totalmente uma estrutura hierárquica usando uma CA para validar certificados.)
Um certificado X.509 é uma coleção de um conjunto padrão de campos contendo informações sobre um usuário ou dispositivo e sua chave pública correspondente. O padrão X.509 define quais informações vão para o certificado e descreve como codificá-lo (o formato dos dados). Todos os certificados X.509 possuem os seguintes dados:
O número da versão X.509
— identifica qual versão do padrão X.509 se aplica a este certificado, o que afeta quais informações podem ser especificadas nele. A mais atual é a versão 3.
A chave pública do titular do certificado
— a chave pública do titular do certificado, juntamente com um identificador de algoritmo que especifica a qual sistema criptográfico a chave pertence e quaisquer parâmetros de chave associados.
O número de série do certificado
— a entidade (aplicação ou pessoa) que criou o certificado é responsável por atribuir-lhe um número de série único para distingui-lo de outros certificados que emite. Esta informação é usada de diversas maneiras; por exemplo, quando um certificado é revogado, seu número de série é colocado em uma Lista de Revogação de Certificados ou CRL.
O identificador exclusivo do detentor do certificado
— (ou DN — nome distinto). Este nome pretende ser exclusivo na Internet. Este nome pretende ser exclusivo na Internet. Um DN consiste em múltiplas subseções e pode ser parecido com isto: CN=Bob Allen, OU=Divisão Total de Segurança de Rede, O=Network Associates, Inc., C=EUA (Referem-se ao nome comum, à unidade organizacional, à organização e ao país do sujeito .)
O período de validade do certificado
— a data/hora de início e a data/hora de expiração do certificado; indica quando o certificado irá expirar.
O nome exclusivo do emissor do certificado
— o nome exclusivo da entidade que assinou o certificado. Normalmente é uma CA. A utilização do certificado implica confiar na entidade que assinou este certificado. (Observe que em alguns casos, como certificados de CA raiz ou de nível superior , o emissor assina seu próprio certificado.)
A assinatura digital do emitente
— a assinatura utilizando a chave privada da entidade que emitiu o certificado.
O identificador do algoritmo de assinatura
— identifica o algoritmo usado pela CA para assinar o certificado.
Existem muitas diferenças entre um certificado X.509 e um certificado PGP, mas as mais importantes são as seguintes: você pode criar seu próprio certificado PGP;
● você deve solicitar e receber um certificado X.509 de uma autoridade de certificação
● Os certificados X.509 suportam nativamente apenas um único nome para o proprietário da chave
● Os certificados X.509 suportam apenas uma única assinatura digital para atestar a validade da chave
Para obter um certificado X.509, você deve solicitar a uma CA a emissão de um certificado. Você fornece sua chave pública, prova de que possui a chave privada correspondente e algumas informações específicas sobre você. Em seguida, você assina digitalmente as informações e envia o pacote completo – a solicitação de certificado – para a CA. A CA então realiza algumas diligências para verificar se as informações fornecidas estão corretas e, em caso afirmativo, gera o certificado e o devolve.
Você pode pensar em um certificado X.509 como um certificado de papel padrão (semelhante ao que você recebeu ao concluir uma aula de primeiros socorros básicos) com uma chave pública colada nele. Ele contém seu nome e algumas informações sobre você, além da assinatura da pessoa que o emitiu para você.
Figura 1-10. Um certificado X.509 Provavelmente, o uso mais visível dos certificados X.509 atualmente é em navegadores da web.
Validade e confiança Cada usuário em um sistema de chave pública está vulnerável a confundir uma chave falsa (certificado) com uma chave real. Validade é a confiança de que um certificado de chave pública pertence ao seu suposto proprietário. A validade é essencial em um ambiente de chave pública onde você deve estabelecer constantemente se um determinado certificado é autêntico ou não. Depois de ter certeza de que um certificado pertencente a outra pessoa é válido, você pode assinar a cópia em seu chaveiro para atestar que verificou o certificado e que ele é autêntico. Se quiser que outras pessoas saibam que você deu ao certificado seu selo de aprovação, você pode exportar a assinatura para um servidor de certificados para que outras pessoas possam vê-la.
Conforme descrito na seção Infraestruturas de Chave Pública , algumas empresas designam uma ou mais Autoridades de Certificação (CAs) para indicar a validade do certificado. Em uma organização que usa uma PKI com certificados X.509, é função da CA emitir certificados aos usuários — um processo que geralmente envolve responder à solicitação de certificado do usuário. Em uma organização que usa certificados PGP sem PKI, é função da CA verificar a autenticidade de todos os certificados PGP e depois assinar os bons. Basicamente, o objetivo principal de uma CA é vincular uma chave pública às informações de identificação contidas no certificado e, assim, garantir a terceiros que algum cuidado foi tomado para garantir que esta ligação das informações de identificação e da chave seja válida. O CA é o Grand Pooh-bah da validação em uma organização; alguém em quem todos confiam e, em algumas organizações, como aquelas que utilizam uma PKI, nenhum certificado é considerado válido, a menos que tenha sido assinado por uma CA confiável.
Verificando validade.
Uma maneira de estabelecer a validade é passar por algum processo manual. Existem várias maneiras de fazer isso. Você pode exigir que o destinatário pretendido lhe entregue fisicamente uma cópia de sua chave pública. Mas isto é muitas vezes inconveniente e ineficiente. Outra forma é verificar manualmente a impressão digital do certificado. Assim como as impressões digitais de cada ser humano são únicas, a impressão digital de cada certificado PGP é única. A impressão digital é um hash do certificado do usuário e aparece como uma das propriedades do certificado. No PGP, a impressão digital pode aparecer como um número hexadecimal ou uma série das chamadas palavras biométricas, que são foneticamente distintas e são usadas para facilitar um pouco o processo de identificação da impressão digital. Você pode verificar se um certificado é válido ligando para o proprietário da chave (para que você origine a transação) e pedindo ao proprietário que leia a impressão digital de sua chave para você e compare essa impressão digital com aquela que você acredita ser a verdadeira. Isso funciona se você conhece a voz do proprietário, mas como verificar manualmente a identidade de alguém que você não conhece? Algumas pessoas colocam a impressão digital de sua chave em seus cartões de visita exatamente por esse motivo. Outra forma de estabelecer a validade do certificado de alguém é confiar que um terceiro indivíduo passou pelo processo de validação do mesmo. Uma CA, por exemplo, é responsável por garantir que, antes de emitir um certificado, ele ou ela o verifique cuidadosamente para ter certeza de que a parte da chave pública realmente pertence ao suposto proprietário. Qualquer pessoa que confie na CA considerará automaticamente quaisquer certificados assinados pela CA como válidos. Outro aspecto da verificação da validade é garantir que o certificado não foi revogado. Para obter mais informações, consulte a seção Revogação de certificado .
Estabelecendo confiança.
Você valida certificados. Você confia nas pessoas. Mais especificamente, você confia nas pessoas para validar os certificados de outras pessoas. Normalmente, a menos que o proprietário lhe entregue o certificado, você terá que confiar na palavra de outra pessoa de que ele é válido.
Introdutores meta e confiáveis.
Na maioria das situações, as pessoas confiam completamente na CA para estabelecer a validade dos certificados. Isso significa que todos os demais dependem da CA para passar por todo o processo de validação manual. Isso é aceitável até um certo número de usuários ou locais de trabalho e, então, não é possível para a AC manter o mesmo nível de validação de qualidade. Nesse caso, é necessário adicionar outros validadores ao sistema.
Um CA também pode ser um meta- introdutor. Um meta-introdutor confere não apenas validade às chaves, mas também confere a capacidade de confiar nas chaves a outros. Semelhante ao rei que entrega seu selo a seus conselheiros de confiança para que eles possam agir de acordo com sua autoridade, o meta-introdutor permite que outros atuem como introdutores de confiança. Esses introdutores confiáveis podem validar chaves com o mesmo efeito do meta-introdutor. Eles não podem, entretanto, criar novos introdutores confiáveis.
Meta-introdutor e introdutor confiável são termos PGP. Em um ambiente X.509, o meta-introdutor é chamado de Autoridade de Certificação raiz ( CA raiz) e os introdutores confiáveis são Autoridades de Certificação subordinadas . A CA raiz usa a chave privada associada a um tipo de certificado especial denominado certificado CA raiz para assinar certificados. Qualquer certificado assinado pelo certificado CA raiz é visto como válido por qualquer outro certificado assinado pela raiz. Este processo de validação funciona mesmo para certificados assinados por outras CAs no sistema — desde que o certificado da CA raiz tenha assinado o certificado da CA subordinada, qualquer certificado assinado pela CA será considerado válido para outras pessoas dentro da hierarquia. Este processo de verificação de backup por meio do sistema para ver quem assinou cujo certificado é chamado de rastreamento de um caminho de certificação ou cadeia de certificação.
Modelos de confiança.
Em sistemas relativamente fechados, como em uma pequena empresa, é fácil rastrear um caminho de certificação até a CA raiz. No entanto, os usuários muitas vezes precisam se comunicar com pessoas fora do seu ambiente corporativo, incluindo algumas que nunca conheceram, como fornecedores, consumidores, clientes, associados e assim por diante. É difícil estabelecer uma linha de confiança com aqueles em quem sua CA não confia explicitamente. As empresas seguem um ou outro modelo de confiança, que determina como os usuários irão estabelecer a validade do certificado. Existem três modelos diferentes:
Confiança Direta.
Confiança Hierárquica Uma teia de confiança Confiança direta A confiança direta é o modelo de confiança mais simples. Neste modelo, um usuário confia que uma chave é válida porque sabe de onde ela veio. Todos os criptosistemas usam essa forma de confiança de alguma forma. Por exemplo, em navegadores da Web, as chaves raiz da Autoridade de Certificação são diretamente confiáveis porque foram enviadas pelo fabricante. Se houver alguma forma de hierarquia, ela se estenderá a partir desses certificados diretamente confiáveis. No PGP, um usuário que valida as chaves e nunca define outro certificado para ser um introdutor confiável está usando confiança direta.
 Figura 1-11. Confiança direta
Figura 1-11. Confiança diretaConfiança Hierárquica.
Em um sistema hierárquico, há vários certificados "raiz" a partir dos quais a confiança se estende. Esses certificados podem certificar eles próprios certificados ou podem certificar certificados que certificam ainda outros certificados em alguma cadeia. Considere isso como uma grande “árvore” de confiança. A validade do certificado "folha" é verificada rastreando desde seu certificador até outros certificadores, até que um certificado raiz diretamente confiável seja encontrado.
Figura 1-12. Confiança hierárquica
Teia de Confiança.
Uma teia de confiança abrange ambos os outros modelos, mas também acrescenta a noção de que a confiança está nos olhos de quem vê (que é a visão do mundo real) e a ideia de que mais informação é melhor. É, portanto, um modelo de confiança cumulativa. Um certificado pode ser confiável diretamente ou confiável em alguma cadeia que remonta a um certificado raiz diretamente confiável (o meta-introdutor) ou por algum grupo de introdutores.
Talvez você já tenha ouvido falar do termo seis graus de separação, que sugere que qualquer pessoa no mundo pode determinar algum vínculo com qualquer outra pessoa no mundo usando seis ou menos outras pessoas como intermediários. Esta é uma teia de introdutores. É também a visão de confiança do PGP. PGP usa assinaturas digitais como forma de introdução. Quando qualquer usuário assina a chave de outro, ele ou ela se torna o introdutor dessa chave. À medida que esse processo avança, ele estabelece uma rede de confiança.
Em um ambiente PGP, qualquer usuário pode atuar como autoridade certificadora. Qualquer usuário PGP pode validar o certificado de chave pública de outro usuário PGP. No entanto, tal certificado só é válido para outro usuário se a parte confiável reconhecer o validador como um introdutor confiável. (Ou seja, você confia na minha opinião de que as chaves dos outros são válidas apenas se você me considerar um apresentador confiável. Caso contrário, minha opinião sobre a validade das outras chaves é discutível.) Armazenados no chaveiro público de cada usuário estão indicadores de
● se o usuário considera ou não uma chave específica válida
● o nível de confiança que o usuário deposita na chave que o proprietário da chave pode servir como certificador das chaves de terceiros
Você indica, na sua cópia da minha chave, se acha que meu julgamento conta. Na verdade, é um sistema de reputação: certas pessoas têm a reputação de fornecer boas assinaturas e as pessoas confiam nelas para atestar a validade de outras chaves.
Níveis de confiança no PGP.
O nível mais alto de confiança em uma chave, a confiança implícita , é a confiança em seu próprio par de chaves. O PGP assume que se você possui a chave privada, você deve confiar nas ações da sua chave pública relacionada. Quaisquer chaves assinadas pela sua chave implicitamente confiável são válidas.
Existem três níveis de confiança que você pode atribuir à chave pública de outra pessoa:
● Confiança total ● Confiança marginal ● Não confiável (ou não confiável)
Para tornar as coisas confusas, também existem três níveis de validade:
● Válido ● Marginalmente válido ● Inválido
Para definir a chave de outra pessoa como um introdutor confiável, você
- Comece com uma chave válida, que seja.
- assinado por você ou
-
assinado por outro apresentador confiável e então
-
Defina o nível de confiança que você acha que o proprietário da chave tem direito.
Por exemplo, suponha que seu chaveiro contenha a chave de Alice. Você validou a chave de Alice e indica isso assinando-a. Você sabe que Alice é uma verdadeira defensora da validação de chaves de outras pessoas. Portanto, você atribui a chave dela com confiança total. Isso faz de Alice uma Autoridade Certificadora. Se Alice assinar a chave de outra pessoa, ela aparecerá como Válida em seu chaveiro. O PGP requer uma assinatura Totalmente confiável ou duas assinaturas Marginalmente confiáveis para estabelecer uma chave como válida. O método do PGP de considerar dois Marginais iguais a um Completo é semelhante a um comerciante que solicita duas formas de identificação. Você pode considerar Alice bastante confiável e também considerar Bob bastante confiável. Qualquer um deles sozinho corre o risco de assinar acidentalmente uma chave falsificada, portanto, você pode não depositar total confiança em nenhum deles. No entanto, as probabilidades de ambos os indivíduos terem assinado a mesma chave falsa são provavelmente pequenas.
Revogação de certificado.
Os certificados só são úteis enquanto são válidos. Não é seguro simplesmente presumir que um certificado é válido para sempre. Na maioria das organizações e em todas as PKIs, os certificados têm uma vida útil restrita. Isso restringe o período em que um sistema fica vulnerável caso ocorra um comprometimento do certificado.
Os certificados são assim criados com um período de validade programado: uma data/hora de início e uma data/hora de expiração. Espera-se que o certificado seja utilizável durante todo o seu período de validade (seu tempo de vida ). Quando o certificado expirar, ele não será mais válido, pois a autenticidade do seu par chave/identificação não estará mais garantida. (O certificado ainda pode ser usado com segurança para reconfirmar informações que foram criptografadas ou assinadas dentro do período de validade – no entanto, ele não deve ser confiável para tarefas criptográficas futuras.)
Existem também situações em que é necessário invalidar um certificado antes da sua data de expiração, como quando o titular do certificado termina o contrato de trabalho com a empresa ou suspeita que a chave privada correspondente do certificado foi comprometida. Isso é chamado de revogação. Um certificado revogado é muito mais suspeito do que um certificado expirado. Os certificados expirados são inutilizáveis, mas não apresentam a mesma ameaça de comprometimento que um certificado revogado. Qualquer pessoa que tenha assinado um certificado pode revogar a sua assinatura no certificado (desde que utilize a mesma chave privada que criou a assinatura). Uma assinatura revogada indica que o signatário não acredita mais que a chave pública e as informações de identificação pertencem uma à outra, ou que a chave pública do certificado (ou a chave privada correspondente) foi comprometida. Uma assinatura revogada deve ter quase tanto peso quanto um certificado revogado. Com certificados X.509, uma assinatura revogada é praticamente igual a um certificado revogado, visto que a única assinatura no certificado é aquela que o tornou válido em primeiro lugar – a assinatura da CA. Os certificados PGP fornecem o recurso adicional de que você pode revogar todo o seu certificado (não apenas as assinaturas nele) se você achar que o certificado foi comprometido. Somente o proprietário do certificado (o detentor da chave privada correspondente) ou alguém que o proprietário do certificado tenha designado como revogador pode revogar um certificado PGP. (Designar um revogador é uma prática útil, pois muitas vezes é a perda da senha da chave privada correspondente do certificado que leva um usuário PGP a revogar seu certificado - uma tarefa que só é possível se alguém tiver acesso à chave privada. ) Somente o emissor do certificado pode revogar um certificado X.509.
Comunicar que um certificado foi revogado.
Quando um certificado é revogado, é importante conscientizar os usuários potenciais do certificado de que ele não é mais válido. Com certificados PGP, a maneira mais comum de comunicar que um certificado foi revogado é publicá-lo em um servidor de certificados para que outras pessoas que desejem se comunicar com você sejam avisadas para não usar essa chave pública. Em um ambiente PKI, a comunicação de certificados revogados é mais comumente obtida por meio de uma estrutura de dados chamada Lista de Revogação de Certificados, ou CRL, que é publicada pela CA. A CRL contém uma lista validada com carimbo de data e hora de todos os certificados revogados e não expirados no sistema. Os certificados revogados permanecem na lista apenas até expirarem e, em seguida, são removidos da lista — isso evita que a lista fique muito longa. A CA distribui a CRL aos usuários em algum intervalo programado regularmente (e potencialmente fora do ciclo, sempre que um certificado é revogado). Teoricamente, isso impedirá que os usuários usem involuntariamente um certificado comprometido. É possível, no entanto, que haja um período de tempo entre as CRLs em que um certificado recentemente comprometido seja usado.
O que é uma senha?
A maioria das pessoas está familiarizada com a restrição de acesso a sistemas de computador por meio de uma senha, que é uma sequência única de caracteres que um usuário digita como código de identificação.
Uma senha longa é uma versão mais longa de uma senha e, em teoria, mais segura. Normalmente composta por várias palavras, uma frase secreta é mais segura contra ataques de dicionário padrão, em que o invasor tenta todas as palavras do dicionário na tentativa de determinar sua senha. As melhores senhas são relativamente longas e complexas e contêm uma combinação de letras maiúsculas e minúsculas, caracteres numéricos e de pontuação. O PGP usa uma senha para criptografar sua chave privada em sua máquina. Sua chave privada é criptografada em seu disco usando um hash de sua senha como chave secreta. Você usa a senha para descriptografar e usar sua chave privada. Uma senha deve ser difícil de esquecer e difícil de ser adivinhada por outras pessoas. Deve ser algo já firmemente enraizado na sua memória de longo prazo, em vez de algo que você invente do zero. Por que? Porque se você esquecer sua senha, você estará sem sorte. Sua chave privada é total e absolutamente inútil sem sua senha e nada pode ser feito a respeito. Lembra-se da citação anterior neste capítulo?
 PGP é a criptografia que manterá os principais governos fora dos seus arquivos. Certamente também o manterá fora de seus arquivos. Tenha isso em mente quando decidir alterar sua senha para a piada daquela piada que você nunca consegue lembrar.
PGP é a criptografia que manterá os principais governos fora dos seus arquivos. Certamente também o manterá fora de seus arquivos. Tenha isso em mente quando decidir alterar sua senha para a piada daquela piada que você nunca consegue lembrar.Divisão de chave.
Dizem que um segredo não é segredo se for conhecido por mais de uma pessoa. Compartilhar um par de chaves privadas representa um grande problema. Embora não seja uma prática recomendada, às vezes é necessário compartilhar um par de chaves privadas. Chaves de assinatura corporativa, por exemplo, são chaves privadas usadas por uma empresa para assinar – por exemplo – documentos legais, informações pessoais confidenciais ou comunicados de imprensa para autenticar sua origem. Nesse caso, vale a pena que vários membros da empresa tenham acesso à chave privada. No entanto, isto significa que qualquer indivíduo pode agir plenamente em nome da empresa. Nesse caso, é aconselhável dividir a chave entre várias pessoas, de modo que mais de uma ou duas pessoas apresentem um pedaço da chave para reconstituí-la em condições utilizáveis. Se poucas peças da chave estiverem disponíveis, a chave ficará inutilizável. Alguns exemplos são dividir uma chave em três partes e exigir duas delas para reconstituir a chave, ou dividi-la em duas partes e exigir ambas as peças. Se uma conexão de rede segura for usada durante o processo de reconstituição, os acionistas da chave não precisam estar fisicamente presentes para aderirem novamente à chave.
-
 @ bc52210b:20bfc6de
2025-04-28 20:13:25
@ bc52210b:20bfc6de
2025-04-28 20:13:25
Imagine a world where clean, safe, and efficient nuclear power can be delivered to any corner of the globe, powering everything from small villages to bustling cities. This vision is becoming a reality with the development of nuclear modular plants—compact, portable nuclear reactors that can be shipped in standard containers and set up quickly to provide reliable energy. These innovative power sources use fission—the process of splitting atomic nuclei to release energy, the same fundamental principle that powers traditional nuclear plants—but with a twist: they utilize thorium as fuel and a molten salt system for cooling and fuel delivery. This combination offers a host of benefits that could revolutionize how we think about nuclear energy.
Portability and Deployment
One of the most significant advantages of these nuclear modular plants is their portability. Designed to fit within standard shipping containers, these reactors can be transported by truck, ship, or even air to virtually any location. This makes them ideal for remote communities, disaster relief efforts, or military operations where traditional power infrastructure is lacking or damaged. Setting up a conventional power plant typically takes years, but these modular units can be operational in a matter of weeks, providing a rapid solution to energy needs.
Safety Features
Safety is a paramount concern in nuclear energy, and modular thorium molten salt reactors (MSRs) offer several inherent safety advantages. Unlike traditional reactors that use water under high pressure, MSRs operate at atmospheric pressure, eliminating the risk of pressure-related accidents. The fuel is dissolved in the molten salt, which means there's no solid fuel that could melt down. If the reactor overheats, the salt expands, naturally slowing the fission reaction—a built-in safety mechanism. Additionally, thorium-based fuels produce less long-lived radioactive waste, reducing the long-term environmental impact.
Efficiency and Abundance
Thorium is a more abundant resource than uranium, with estimates suggesting it is three to four times more plentiful in the Earth's crust. This abundance makes thorium a sustainable fuel choice for the future. Moreover, MSRs can operate at higher temperatures than traditional reactors, leading to greater thermal efficiency. This means more electricity can be generated from the same amount of fuel, making the energy production process more efficient and cost-effective in the long run.
Scalability
The modular design of these reactors allows for scalability to meet varying power demands. A single unit might power a small community, while multiple units can be combined to serve larger towns or cities. This flexibility is particularly useful for growing populations or regions with fluctuating energy needs. As demand increases, additional modules can be added without the need for extensive new infrastructure.
Cost-Effectiveness
While the initial investment in nuclear modular plants may be significant, the long-term operational costs can be lower than traditional power sources. The high efficiency of MSRs means less fuel is needed over time, and the reduced waste production lowers disposal costs. Additionally, the ability to mass-produce these modular units could drive down manufacturing costs, making nuclear power more accessible and affordable.
Environmental Impact
Nuclear power is already one of the cleanest energy sources in terms of carbon emissions, and thorium MSRs take this a step further. By producing less long-lived waste and utilizing a more abundant fuel, these reactors offer a more sustainable path for nuclear energy. Furthermore, their ability to provide reliable baseload power can help reduce reliance on fossil fuels, contributing to global efforts to combat climate change.
Challenges and Considerations
Despite these benefits, there are challenges to overcome before nuclear modular plants can be widely deployed. The technology for thorium MSRs is still in the developmental stage, with ongoing research needed to address issues such as material corrosion and fuel processing. Regulatory frameworks will also need to adapt to this new type of reactor, and public perception of nuclear energy remains a hurdle in many regions. However, with continued investment and innovation, these obstacles can be addressed.
Conclusion
In conclusion, nuclear modular plants using thorium and molten salt systems represent a promising advancement in nuclear technology. Their portability, safety features, efficiency, scalability, and environmental benefits make them an attractive option for meeting the world's growing energy needs. While challenges remain, the potential of these reactors to provide clean, reliable power to communities around the globe is undeniable. As research and development continue, we may soon see a new era of nuclear energy that is safer, more efficient, and more accessible than ever before.
-
 @ c3b2802b:4850599c
2025-04-29 06:48:44
@ c3b2802b:4850599c
2025-04-29 06:48:44Haben Sie schon einmal einen Intelligenztest gemacht? Da geht es darum, in beschränkter Zeit eine Vielfalt rationaler Denkprozesse so präzise wie möglich korrekt zu absolvieren, wenn man gern einen hohen Intelligenzquotienten bescheinigt haben mag. Unsere gesamte Schulbildung ist überwiegend auf die Entfaltung dieser Art kognitiver Potentiale ausgerichtet. Allerdings ist es weniger eigenständiges Denken, das im Fokus steht. Meist handelt es sich um "betreutes" Denken in vorgegebenen begrifflichen Kategorien und mit vorgegebenen Frage-Antwort Schemata, welche vorab zu pauken sind, wenn man bestehen möchte.
Und wie steht es um das Mitfühlen mit anderen Geschöpfen - mit Grashüpfern, Ameisen, Pflanzen, Fischen, Schweinen oder Rindern? Und wie ist es um das Mitfühlen mit Menschen bestellt, welche infolge von Kriegshandlungen schwerste körperliche und seelische Schäden davontragen oder sterben? Wurden solche Fragen in Ihrer Ausbildung thematisiert? Meine Erinnerung bringt das Sezieren von Fröschen und Fischen im Biologieunterricht hervor, wobei Fragen an die Lehrer nach dem Leiden der Tiere als unpassend abgetan wurden. Die Überlebenden unserer Vorfahren in den Weltkriegen nach den erlittenen Leiden zu fragen: Hat Sie dazu einer Ihrer Lehrer oder Professoren ermutigt?
Sollten Sie bis hierher mitschwingen und ähnlich empfinden, dass unser Potential zum Mitfühlen in unserer Gesellschaft gegenüber kognitiven Potentialen wenig kultiviert und gepflegt wird, dann könnte sich ein Pfad auftun, unsere entstehende Regionalgesellschaft zu stärken.
Wenn wir unsere Sinneskanäle öffnen für das Befinden der Schöpfung, in der wir uns gerade bewegen, erschließen sich große Energiequellen. Diese können uns dienen, aus der vom hypertrophierten Denken entstellten Welt zurück in unsere Mitte zu finden. Zum einen können wir wahrnehmen, wie das Leben in und um uns pulsiert, können mitfühlen in dem zauberhaften Geschehen, das wir in besonderer Weise im gerade erwachenden Frühjahr erleben dürfen. Zum anderen werden wir Geschöpfe in Not oder Bedrängnis wahrnehmen und können so erfahren, dass es auch uns selbst wohl tut, wenn wir uns für diese engagieren. Wer schon einmal ein Tier geheilt hat oder sich für Opfer von Gewalthandlungen eingesetzt hat, kennt das.
Diese unmittelbaren Energiequellen geben uns Kraft, Bestätigung und Befriedigung - und diese Energie kann jeder Mensch zu jeder Zeit seines Lebens anzapfen.
Voraussetzung ist lediglich, dass wir die gewohnten "betreuten" Denkprozesse, auf die wir programmiert wurden, lernen zu unterbrechen. Dass wir die begriffliche Diarrhoe und Bedeutungsverdrehung seitens gefühlsarmer oder gefühlloser Menschen und ihrer Lakaien, welche uns aktuell zu Kriegshandlungen animieren wollen, hinter uns lassen. Dass wir uns nicht wie in den 1930er Jahren mit Worten wie "Kriegstüchtigkeit" gegen andere Völker aufhetzen lassen. Wenn wir solchen verbalen Entgleisungen nicht länger Aufmerksamkeit schenken, schaffen wir Zeit und Raum für das Mitfühlen.
Das Mitfühlen gibt uns ethische Orientierung, zeigt Wege auf, unsere Bestimmung zu finden und gibt uns die Kraft, unser Leben nach unseren Wertvorstellungen zu gestalten. Es beantwortet uns Fragen nach dem WOHIN und WOZU.
Das selbst Denken ist ein Werkzeug, welches uns, nachdem wir in unsere Mitte gefunden haben, dazu dienen kann, die Frage nach dem WIE zu klären.
Mit gleichgesinnten mitfühlenden und selbst denkenden Menschen ist es möglich, an unserer Regionalgesellschaft zu werkeln und funktionierende, auf Vertrauen basierende Initiativen und Gemeinschaften zum Blühen zu bringen. In meinen Blogbeiträgen sind seit 2018 einige davon beschrieben. Und ein psychologischer Zusammenhang scheint bemerkenswert: In solchen Gemeinschaften fühlen sich auch die Beteiligten wohl. Dazu liegen wissenschaftliche Studien vor, welche Sie in meinem Publikationsverzeichnis finden.
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ c1e6505c:02b3157e
2025-04-28 01:58:55
@ c1e6505c:02b3157e
2025-04-28 01:58:55This is a long form test note from Untype.app
Seems like this could work well.
Here is a photograph of the infamous red firebird that has been in the same spot for over 10 years.
There is a header image up top as well. Will that be seen? Maybe?
Clean interface and you're able to type and see a preview window of what your post would like. Cool!
Text before the image prompt makes this lettering large and bold.

Here is a line break
Let me know if you can see this text that is now under the image.
BYE (IN BOLD)!
-
 @ e516ecb8:1be0b167
2025-04-28 19:56:30
@ e516ecb8:1be0b167
2025-04-28 19:56:30El Gran Apagón y la Tormenta Perfecta: ¿Hacia Dónde Nos Llevan?
Recientemente, un corte de luz masivo dejó a oscuras a España, Portugal y parte de Francia. Como suele pasar cuando las explicaciones escasean o no se quieren dar, la narrativa oficial apuntó al cambio climático. Un artículo de ABC sugiere que una "vibración atmosférica inducida" por "variaciones extremas de temperatura" podría ser la culpable (ABC, 28/04/2025). Pero, ¿es realmente el calentamiento global el villano de esta historia, o estamos ante un síntoma de algo más grande y complejo?
Una Red de Decisiones Interconectadas
Nada ocurre en el vacío, y este apagón no es una excepción. La generación de electricidad, cada vez más dependiente de fuentes renovables no convencionales, enfrenta retos de estabilidad y costos crecientes. A esto se suma la presión política para transformar nuestras vidas bajo la bandera de la sostenibilidad. Por ejemplo, la idea de la "ciudad de 15 minutos", donde todo lo que necesitas está a un corto paseo o pedaleo, suena ideal. Pero en lugares como el Reino Unido, esta visión viene acompañada de cámaras de vigilancia que controlan tus movimientos, justificadas por la "seguridad" o la "eficiencia".
Mientras tanto, la Unión Europea avanza hacia un futuro donde, para 2030, todos los autos deberán ser eléctricos. Con una red eléctrica inestable y precios de energía disparados, ¿cómo se supone que cargaremos esos vehículos? La respuesta parece ser: no lo hagas. Muévete en bicicleta, quédate cerca de casa. La movilidad, un símbolo de libertad, se está restringiendo para las masas, mientras la élite política y corporativa sigue surcando los cielos en jets privados para "combatir el cambio climático" o, como Bernie Sanders y AOC, para denunciar la oligarquía desde sus podios privilegiados.
Dependencia Eléctrica: Una Trampa Silenciosa
La electrificación no se detiene en los autos. Los edificios modernos tienden a ser completamente eléctricos, y en algunos lugares ya se habla de prohibir las cocinas a gas. Imagina un futuro donde dependes de la red eléctrica para cocinar una simple salchicha. Ahora, suma un apagón como el reciente. Sin electricidad, no hay cena, no hay calefacción, no hay nada. La automatización total, que nos venden como progreso, nos hace más vulnerables a estos colapsos.
El Euro Digital: Control Absoluto
La Unión Europea también está empujando el euro digital, una moneda que promete conveniencia, pero a un costo altísimo. Con ella, cada transacción será rastreable, y las autoridades podrían restringir su uso para ciertos fines o incluso "quemar" euros digitales a voluntad para controlar su valor frente a otras monedas. ¿Qué pasa con la libertad financiera? ¿Qué pasa con la privacidad? Este sistema, combinado con una red eléctrica frágil, pinta un panorama donde el ciudadano promedio queda atrapado en una jaula tecnológica.
Criptomonedas, Efectivo y Oro: ¿Alternativas Reales?
Las criptomonedas, que muchos ven como una salida, también son vulnerables a los cortes de energía. Sin electricidad, no hay blockchain. El efectivo, por su parte, sigue siendo una opción, pero se desgasta, pierde valor con la inflación y, en muchos lugares, está siendo demonizado en favor de pagos digitales. Luego está el oro, el refugio histórico. Pero incluso aquí hay trampas: viajar con oro puede convertirte en sospechoso en un aeropuerto, obligado a explicar el origen de tu propiedad. ¿Desde cuándo debemos justificar lo que es nuestro? ¿Dónde quedó la presunción de inocencia?
"No Tendrás Nada y Serás Feliz"
Cuando uno conecta los puntos —apagones, electrificación forzada, monedas digitales, restricciones de movilidad— es difícil no pensar en el famoso eslogan atribuido al Foro Económico Mundial: "No tendrás nada y serás feliz". Mencionarlo te hace ganar el sello de "conspiranóico", pero las señales están ahí. La pregunta es: ¿estamos caminando hacia un futuro de control total disfrazado de sostenibilidad, o es solo una serie de coincidencias desafortunadas?
-
 @ 78b3c1ed:5033eea9
2025-04-27 01:42:48
@ 78b3c1ed:5033eea9
2025-04-27 01:42:48・ThunderHubで焼いたマカロンがlncli printmacaroonでどう見えるか確認した。
ThunderHub macaroon permissions
get invoices invoices:read create invoices invoices:write get payments offchain:read pay invoices offchain:write get chain transactions onchain:read send to chain address onchain:write create chain address address:write get wallet info info:read stop daemon info:write この結果によれば、offchain:wirteとonchain:writeの権限がなければそのマカロンを使うクライアントは勝手にBTCを送金することができない。 info:writeがなければ勝手にLNDを止めたりすることができない。
・lncli printmacaroonでデフォルトで作られるmacaroonのpermissionsを調べてみた。 admin.macaroon
{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "address:read", "address:write", "info:read", "info:write", "invoices:read", "invoices:write", "macaroon:generate", "macaroon:read", "macaroon:write", "message:read", "message:write", "offchain:read", "offchain:write", "onchain:read", "onchain:write", "peers:read", "peers:write", "signer:generate", "signer:read" ], "caveats": null }chainnotifier.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "onchain:read" ], "caveats": null }invoice.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "address:read", "address:write", "invoices:read", "invoices:write", "onchain:read" ], "caveats": null }invoices.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "invoices:read", "invoices:write" ], "caveats": null }readonly.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "address:read", "info:read", "invoices:read", "macaroon:read", "message:read", "offchain:read", "onchain:read", "peers:read", "signer:read" ], "caveats": null }router.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "offchain:read", "offchain:write" ], "caveats": null }signer.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "signer:generate", "signer:read" ], "caveats": null }walletkit.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "address:read", "address:write", "onchain:read", "onchain:write" ], "caveats": null }・lncli listpermissions コマンドですべての RPC メソッド URI と、それらを呼び出すために必要なマカロン権限を一覧表示できる。 LND v0.18.5-betaでやると1344行ほどのJSONができる。 AddInvoiceだとinvoice:writeのpermissionを持つmacaroonを使えばインボイスを作れるようだ。
"/lnrpc.Lightning/AddInvoice": { "permissions": [ { "entity": "invoices", "action": "write" } ] },lncli listpermissionsからentityとactionを抜き出してみた。 ``` "entity": "address", "entity": "info", "entity": "invoices", "entity": "macaroon", "entity": "message", "entity": "offchain", "entity": "onchain", "entity": "peers", "entity": "signer","action": "generate" "action": "read" "action": "write"
lncli とjqを組み合わせると例えば以下コマンドでinvoices:writeを必要とするRPCの一覧を表示できる。 invoices:writeだとAddInvoiceの他にホドルインボイス作成でも使ってるようだlncli listpermissions | jq -r '.method_permissions | to_entries[] | select(.value.permissions[] | select(.entity == "invoices" and .action == "write")) | .key'/invoicesrpc.Invoices/AddHoldInvoice /invoicesrpc.Invoices/CancelInvoice /invoicesrpc.Invoices/HtlcModifier /invoicesrpc.Invoices/LookupInvoiceV2 /invoicesrpc.Invoices/SettleInvoice /lnrpc.Lightning/AddInvoiceinvoices:readだと以下となる。/invoicesrpc.Invoices/SubscribeSingleInvoice /lnrpc.Lightning/ListInvoices /lnrpc.Lightning/LookupInvoice /lnrpc.Lightning/SubscribeInvoicesLNの主だった機能のRPCはoffchainが必要ぽいので抜き出してみた。 offchain:write チャネルの開閉、ペイメントの送信までやってるみたい。 デフォルトのmacaroonでoffchain:writeを持ってるのはadminとrouterの2つだけ。openchannel,closechannelはonchain:writeのpermissionも必要なようだ。/autopilotrpc.Autopilot/ModifyStatus /autopilotrpc.Autopilot/SetScores /lnrpc.Lightning/AbandonChannel /lnrpc.Lightning/BatchOpenChannel /lnrpc.Lightning/ChannelAcceptor /lnrpc.Lightning/CloseChannel /lnrpc.Lightning/DeleteAllPayments /lnrpc.Lightning/DeletePayment /lnrpc.Lightning/FundingStateStep /lnrpc.Lightning/OpenChannel /lnrpc.Lightning/OpenChannelSync /lnrpc.Lightning/RestoreChannelBackups /lnrpc.Lightning/SendCustomMessage /lnrpc.Lightning/SendPayment /lnrpc.Lightning/SendPaymentSync /lnrpc.Lightning/SendToRoute /lnrpc.Lightning/SendToRouteSync /lnrpc.Lightning/UpdateChannelPolicy /routerrpc.Router/HtlcInterceptor /routerrpc.Router/ResetMissionControl /routerrpc.Router/SendPayment /routerrpc.Router/SendPaymentV2 /routerrpc.Router/SendToRoute /routerrpc.Router/SendToRouteV2 /routerrpc.Router/SetMissionControlConfig /routerrpc.Router/UpdateChanStatus /routerrpc.Router/XAddLocalChanAliases /routerrpc.Router/XDeleteLocalChanAliases /routerrpc.Router/XImportMissionControl /wtclientrpc.WatchtowerClient/AddTower /wtclientrpc.WatchtowerClient/DeactivateTower /wtclientrpc.WatchtowerClient/RemoveTower /wtclientrpc.WatchtowerClient/TerminateSession"/lnrpc.Lightning/OpenChannel": { "permissions": [ { "entity": "onchain", "action": "write" }, { "entity": "offchain", "action": "write" } ] },offchain:read readの方はチャネルやインボイスの状態を確認するためのpermissionのようだ。/lnrpc.Lightning/ChannelBalance /lnrpc.Lightning/ClosedChannels /lnrpc.Lightning/DecodePayReq /lnrpc.Lightning/ExportAllChannelBackups /lnrpc.Lightning/ExportChannelBackup /lnrpc.Lightning/FeeReport /lnrpc.Lightning/ForwardingHistory /lnrpc.Lightning/GetDebugInfo /lnrpc.Lightning/ListAliases /lnrpc.Lightning/ListChannels /lnrpc.Lightning/ListPayments /lnrpc.Lightning/LookupHtlcResolution /lnrpc.Lightning/PendingChannels /lnrpc.Lightning/SubscribeChannelBackups /lnrpc.Lightning/SubscribeChannelEvents /lnrpc.Lightning/SubscribeCustomMessages /lnrpc.Lightning/VerifyChanBackup /routerrpc.Router/BuildRoute /routerrpc.Router/EstimateRouteFee /routerrpc.Router/GetMissionControlConfig /routerrpc.Router/QueryMissionControl /routerrpc.Router/QueryProbability /routerrpc.Router/SubscribeHtlcEvents /routerrpc.Router/TrackPayment /routerrpc.Router/TrackPaymentV2 /routerrpc.Router/TrackPayments /wtclientrpc.WatchtowerClient/GetTowerInfo /wtclientrpc.WatchtowerClient/ListTowers /wtclientrpc.WatchtowerClient/Policy /wtclientrpc.WatchtowerClient/Stats・おまけ1 RPCメソッド名にopenを含む要素を抽出するコマンドlncli listpermissions | jq '.method_permissions | to_entries[] | select(.key | test("open"; "i"))'{ "key": "/lnrpc.Lightning/BatchOpenChannel", "value": { "permissions": [ { "entity": "onchain", "action": "write" }, { "entity": "offchain", "action": "write" } ] } } { "key": "/lnrpc.Lightning/OpenChannel", "value": { "permissions": [ { "entity": "onchain", "action": "write" }, { "entity": "offchain", "action": "write" } ] } } { "key": "/lnrpc.Lightning/OpenChannelSync", "value": { "permissions": [ { "entity": "onchain", "action": "write" }, { "entity": "offchain", "action": "write" } ] } }・おまけ2 thunderhubで作ったmacaroonはテキストで出力されコピペして使うもので、macaroonファイルになってない。 HEXをmacaroonファイルにするには以下コマンドでできる。HEXをコピペして置換する。またYOURSの箇所を自分でわかりやすい名称に置換すると良い。echo -n "HEX" | xxd -r -p > YOURS.macaroonthunderhubで"Create Invoices, Get Invoices, Get Wallet Info, Get Payments, Pay Invoices"をチェックして作ったmacaroonのpermissionsは以下となる。{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "info:read", "invoices:read", "invoices:write", "offchain:read", "offchain:write" ], "caveats": null } ``` offchain:writeはあるがonchain:writeがないのでチャネル開閉はできないはず。 -
 @ f32184ee:6d1c17bf
2025-04-23 13:21:52
@ f32184ee:6d1c17bf
2025-04-23 13:21:52Ads Fueling Freedom
Ross Ulbricht’s "Decentralize Social Media" painted a picture of a user-centric, decentralized future that transcended the limitations of platforms like the tech giants of today. Though focused on social media, his concept provided a blueprint for decentralized content systems writ large. The PROMO Protocol, designed by NextBlock while participating in Sovereign Engineering, embodies this blueprint in the realm of advertising, leveraging Nostr and Bitcoin’s Lightning Network to give individuals control, foster a multi-provider ecosystem, and ensure secure value exchange. In this way, Ulbricht’s 2021 vision can be seen as a prescient prediction of the PROMO Protocol’s structure. This is a testament to the enduring power of his ideas, now finding form in NextBlock’s innovative approach.
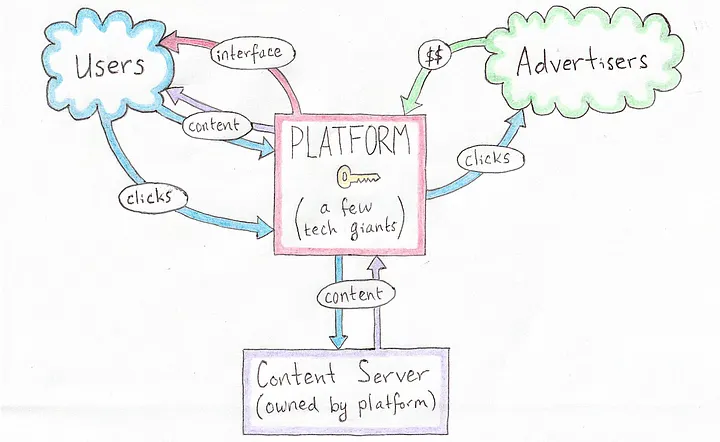 [Current Platform-Centric Paradigm, source: Ross Ulbricht's Decentralize Social Media]
[Current Platform-Centric Paradigm, source: Ross Ulbricht's Decentralize Social Media]Ulbricht’s Vision: A Decentralized Social Protocol
In his 2021 Medium article Ulbricht proposed a revolutionary vision for a decentralized social protocol (DSP) to address the inherent flaws of centralized social media platforms, such as privacy violations and inconsistent content moderation. Writing from prison, Ulbricht argued that decentralization could empower users by giving them control over their own content and the value they create, while replacing single, monolithic platforms with a competitive ecosystem of interface providers, content servers, and advertisers. Though his focus was on social media, Ulbricht’s ideas laid a conceptual foundation that strikingly predicts the structure of NextBlock’s PROMO Protocol, a decentralized advertising system built on the Nostr protocol.
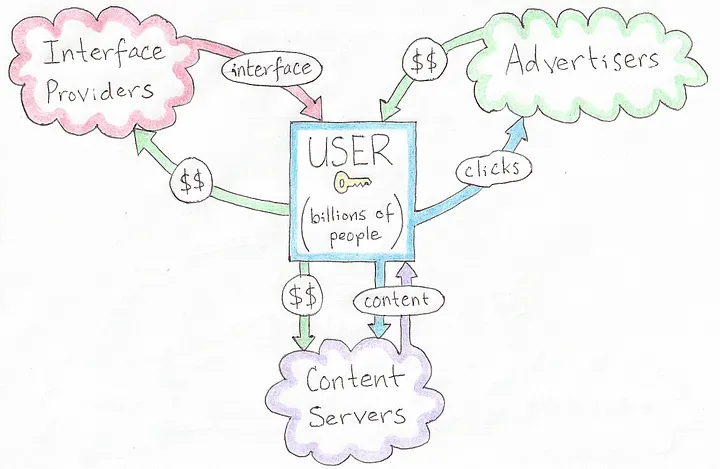 [A Decentralized Social Protocol (DSP), source: Ross Ulbricht's Decentralize Social Media]
[A Decentralized Social Protocol (DSP), source: Ross Ulbricht's Decentralize Social Media]Ulbricht’s Principles
Ulbricht’s article outlines several key principles for his DSP: * User Control: Users should own their content and dictate how their data and creations generate value, rather than being subject to the whims of centralized corporations. * Decentralized Infrastructure: Instead of a single platform, multiple interface providers, content hosts, and advertisers interoperate, fostering competition and resilience. * Privacy and Autonomy: Decentralized solutions for profile management, hosting, and interactions would protect user privacy and reduce reliance on unaccountable intermediaries. * Value Creation: Users, not platforms, should capture the economic benefits of their contributions, supported by decentralized mechanisms for transactions.
These ideas were forward-thinking in 2021, envisioning a shift away from the centralized giants dominating social media at the time. While Ulbricht didn’t specifically address advertising protocols, his framework for decentralization and user empowerment extends naturally to other domains, like NextBlock’s open-source offering: the PROMO Protocol.
NextBlock’s Implementation of PROMO Protocol
The PROMO Protocol powers NextBlock's Billboard app, a decentralized advertising protocol built on Nostr, a simple, open protocol for decentralized communication. The PROMO Protocol reimagines advertising by: * Empowering People: Individuals set their own ad prices (e.g., 500 sats/minute), giving them direct control over how their attention or space is monetized. * Marketplace Dynamics: Advertisers set budgets and maximum bids, competing within a decentralized system where a 20% service fee ensures operational sustainability. * Open-Source Flexibility: As an open-source protocol, it allows multiple developers to create interfaces or apps on top of it, avoiding the single-platform bottleneck Ulbricht critiqued. * Secure Payments: Using Strike Integration with Bitcoin Lightning Network, NextBlock enables bot-resistant and intermediary-free transactions, aligning value transfer with each person's control.
This structure decentralizes advertising in a way that mirrors Ulbricht’s broader vision for social systems, with aligned principles showing a specific use case: monetizing attention on Nostr.
Aligned Principles
Ulbricht’s 2021 article didn’t explicitly predict the PROMO Protocol, but its foundational concepts align remarkably well with NextBlock's implementation the protocol’s design: * Autonomy Over Value: Ulbricht argued that users should control their content and its economic benefits. In the PROMO Protocol, people dictate ad pricing, directly capturing the value of their participation. Whether it’s their time, influence, or digital space, rather than ceding it to a centralized ad network. * Ecosystem of Providers: Ulbricht envisioned multiple providers replacing a single platform. The PROMO Protocol’s open-source nature invites a similar diversity: anyone can build interfaces or tools on top of it, creating a competitive, decentralized advertising ecosystem rather than a walled garden. * Decentralized Transactions: Ulbricht’s DSP implied decentralized mechanisms for value exchange. NextBlock delivers this through the Bitcoin Lightning Network, ensuring that payments for ads are secure, instantaneous and final, a practical realization of Ulbricht’s call for user-controlled value flows. * Privacy and Control: While Ulbricht emphasized privacy in social interactions, the PROMO Protocol is public by default. Individuals are fully aware of all data that they generate since all Nostr messages are signed. All participants interact directly via Nostr.
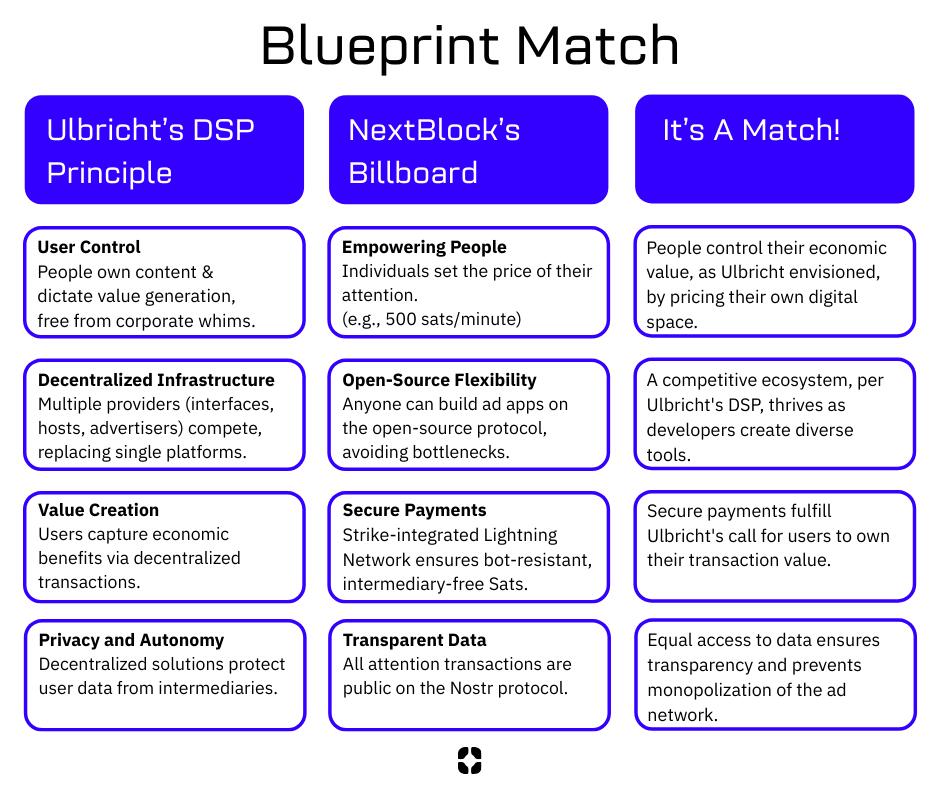 [Blueprint Match, source NextBlock]
[Blueprint Match, source NextBlock]
Who We Are
NextBlock is a US-based new media company reimagining digital ads for a decentralized future. Our founders, software and strategy experts, were hobbyist podcasters struggling to promote their work online without gaming the system. That sparked an idea: using new tech like Nostr and Bitcoin to build a decentralized attention market for people who value control and businesses seeking real connections.
Our first product, Billboard, is launching this June.
Open for All
Our model’s open-source! Check out the PROMO Protocol, built for promotion and attention trading. Anyone can join this decentralized ad network. Run your own billboard or use ours. This is a growing ecosystem for a new ad economy.
Our Vision
NextBlock wants to help build a new decentralized internet. Our revolutionary and transparent business model will bring honest revenue to companies hosting valuable digital spaces. Together, we will discover what our attention is really worth.
Read our Manifesto to learn more.
NextBlock is registered in Texas, USA.
-
 @ de6c63ab:d028389b
2025-04-28 12:20:45
@ de6c63ab:d028389b
2025-04-28 12:20:45Honestly, I didn’t think this would still be a thing in 2025, but every once in a while it pops up again:
“Bitcoin? Uh, I don’t know… but blockchain, now that could be useful! 🤌”
“Blockchain is one of the most important technologies of our time. Maybe you know it from crypto, but it’s so much more. It’s a way to store and verify data securely, transparently, and without a middleman. That’s why it’s going to revolutionize banking, healthcare, logistics, and even government!”
“Blockchain is transforming how we store, share, and verify information. Its benefits go far beyond cryptocurrencies. Understanding it today means preparing for tomorrow, because blockchain is guaranteed to play a major role in the future.”

Blockchain
When people say "blockchain," they usually mean the bitcoin database — with all its unique properties — even when they’re imagining using it elsewhere.
But here’s the thing: blockchain by itself isn’t some revolutionary breakthrough.
Stripped from bitcoin, it’s just a fancy list of records, each pointing to the previous one with a reference (typically a hash).
That's it.This idea — chaining data together — isn’t new.
It goes back to at least 1991, when Haber and Stornetta proposed it for timestamping documents.By itself, blockchain isn’t secure (you can always rewrite past records if you recompute the chain), isn’t necessarily transparent (the data can be encrypted or hidden), and doesn't magically remove the need for trust (if someone logs soccer scores into a blockchain, you still have to trust they reported the results honestly).
What actually makes bitcoin’s blockchain secure and trustworthy is the system around it — the economic incentives, the ruthless competition for block rights, and the distributed consensus mechanics.
Without those, blockchain is just another database.
How Does Bitcoin Make It Work?
To understand why, we need to zoom in a little.
Superficially, bitcoin’s blockchain looks like a simple ledger — a record of transactions grouped into blocks. A transaction means someone spent bitcoin — unlocking it and locking it up again for someone else.
But here’s the key:
Every participant can independently verify whether each transaction is valid, with no outside help and no trust required.Think of every transaction like a math equation.
Something like: x + 7 = 5, with the solution x = -2.
You don’t need anyone to tell you if it’s correct — you can check it yourself.Of course, bitcoin’s equations are far more complex.
They involve massive numbers and strange algebraic structures, where solving without the right key is practically impossible, but verifying a solution is easy.This is why only someone with the private key can authorize a transaction.
In a way, "solving" these equations is how you prove your right to spend bitcoin.
Ownership and transfers are purely a matter of internal system math — no external authority needed.
Could We Use Blockchain for Other Stuff?
Could we use a blockchain to independently verify medical records, soccer scores, or property ownership?
No.
Blockchain can't magically calculate whether you broke your arm, whether Real Madrid tied against Barcelona, or who owns a cottage in some village.
It can verify that someone owns bitcoin at a particular address, because that's just solving equations inside the system.
But anything that depends on outside facts?
Blockchain can't help you there.
Why Does Everyone Stick to One Version?
Another big question:
Why do people in bitcoin agree on the same version of history?Because of proof-of-work.
To add a new block, you have to find a specific giant number — the nonce — that, together with the block’s contents, satisfies a predefined condition.
You can't calculate the nonce directly — you have to guess, billions of times per second, until you hit the jackpot.
It takes minutes of relentless effort.An invalid transaction would invalidate the entire block, wasting all the miner’s effort.
If the block is valid, the miner earns a reward — newly minted bitcoins plus transaction fees — making the massive effort worthwhile.
And importantly, because each block is built on top of all previous ones, rewriting history would mean redoing all the proof-of-work from that point forward — an astronomically expensive and practically impossible task.
The deeper a block is buried under newer blocks, the more secure it becomes — making the past effectively immutable.And again: each node independently verifies all transactions.
Miners don't create truth; they race to package and timestamp already-valid transactions.
The winning chain is simply the one with the most provable work behind it.
Bitcoin and Blockchain: Inseparable
Bitcoin is created on the blockchain — and it exists only within the blockchain.
Ownership is defined by it.
The decentralized management of the blockchain is driven by bitcoin incentives — the pursuit of something scarce, hard-earned, and impossible to fake.No blockchain, no bitcoin.
No bitcoin, no meaningful blockchain.
Can We Just Blockchain Everything?
Alright, so what happens if we try to apply this system to something else — say, a land registry?
Properties themselves don’t "exist" on a blockchain — only claims about them can be recorded.
But who writes the claims? Random miners?
Where do they get their information?
They can’t compute it from previous blocks.
They’d have to physically go check who owns what.What if they’re lazy? Lied to? Made mistakes?
How would anyone else verify the records?
Ownership in the physical world isn’t a problem you can solve by crunching numbers in a database.Suddenly, we’re right back to needing trusted third parties — the very thing blockchain was supposed to eliminate.
And if there’s a dispute?
Say someone refuses to leave a house, claiming they've lived there forever.
Is the blockchain going to show up and evict them?Of course not.
Blockchain Without Bitcoin Is Just a Data Structure
And that’s the difference.
When blockchain is part of bitcoin’s closed system, it works because everything it cares about is internal and verifiable.
When you try to export blockchain into the real world — without bitcoin — it loses its magic.
Blockchain-like structures actually exist elsewhere too — take Git, for example.
It’s a chain of commits, each referencing the previous one by its hash.
It chains data like a blockchain does — but without the security, decentralization, or economic meaning behind bitcoin.Blockchain is just a data structure.
Bitcoin is what gives it meaning.In bitcoin, the blockchain is not just a ledger — it's a trustless system of property rights enforced by math and energy, without any central authority.
-
 @ f683e870:557f5ef2
2025-04-28 10:10:55
@ f683e870:557f5ef2
2025-04-28 10:10:55Spam is the single biggest problem in decentralized networks. Jameson Lopp, co-founder of Casa and OG bitcoiner, has written a brilliant article on the death of decentralized email that paints a vivid picture of what went wrong—and how an originally decentralized protocol was completely captured. The cause? Spam.
The same fate may happen to Nostr, because posting a note is fundamentally cheap. Payments, and to some extent Proof of Work, certainly have their role in fighting spam, but they introduce friction, which doesn’t work everywhere. In particular, they can’t solve every economic problem.\ Take free trials, for example. There is a reason why 99% of companies offer them. Sure, you waste resources on users who don’t convert, but it’s a calculated cost, a marketing expense. Also, some services can’t or don’t want to monetize directly. They offer something for free and monetize elsewhere.
So how do you offer a free trial or giveaway in a hostile decentralized network? Or even, how do you decide which notes to accept on your relay?
At first glance, these may seem like unrelated questions—but they’re not. Generally speaking, these are situations where you have a finite budget, and you want to use it well. You want more of what you value — and less of what you don’t (spam).
Reputation is a powerful shortcut when direct evaluation isn’t practical. It’s hard to earn, easy to lose — and that’s exactly what makes it valuable.\ Can a reputable user do bad things? Absolutely. But it’s much less likely, and that’s the point. Heuristics are always imperfect, just like the world we live in.
The legacy Web relies heavily on email-based reputation. If you’ve ever tried to log in with a temporary email, you know what I’m talking about. It just doesn’t work anymore. The problem, as Lopp explains, is that these systems are highly centralized, opaque, and require constant manual intervention.\ They also suck. They put annoying roadblocks between the world and your product, often frustrating the very users you’re trying to convert.
At Vertex, we take a different approach.\ We transparently analyze Nostr’s open social graph to help companies fight spam while improving the UX for their users. But we don’t take away your agency—we just do the math. You take the decision of what algorithm and criteria to use.
Think of us as a signal provider, not an authority.\ You define what reputation means for your use case. Want to rank by global influence? Local or personalized? You’re in control. We give you actionable and transparent analytics so you can build sharper filters, better user experiences, and more resilient systems. That’s how we fight spam, without sacrificing decentralization.
Are you looking to add Web of Trust capabilities to your app or project?\ Take a look at our website or send a DM to Pip.
-
 @ fe02e8ec:f07fbe0b
2025-04-28 21:23:01
@ fe02e8ec:f07fbe0b
2025-04-28 21:23:01Die baldige Ex-Außenministerin Annalena Baerbock fordert einen radikalen Wandel in der Energieversorgung hin zu einer feministischen Energiepolitik. Wie sich gezeigt habe, so sei das spanische Netz am 28.04.25 wegen toxischer Männlichkeit zusammengebrochen. Es hätte sich herausgestellt, dass alle Überlandleitungen von Männern gebaut und installiert worden waren! Dies, so Baerbock, sei ein untragbarer Zustand, der durch den resultierenden Blackout für viel Leid und Ärger gesorgt habe. Selbst Haarföhns waren nicht mehr in Betrieb zu nehmen!
«Nur Frauen sind in der Lage, derart empfindliche und sensible Ströme zu leiten. Denn Strömen liegt in ihrer Natur. Sie benötigen keine Messgeräte oder teure Transformatoren für die Strömung, da Mutter Natur – eine Frau, wie der Name schon sagt – für alles selbst sorgen wird. Man muss nur verhindern, dass maskuline Energien verströmt werden, die nämlich den Strom um 360 Grad drehen würden.»
Mit dieser Analyse empfiehlt sich Annalena B. nicht nur für höchste UN Ämter sondern ebenfalls für den Vorsitz des Weltklimarates IPCC. Aus informierten Kreisen ist zu hören, dass sie nur noch die Papstwahl abwarten möchte - schließlich wäre es Zeit für eine Päpstin - bis sie sich fürs Klima bewerben würde. Um weitere Blackouts abzuschrecken überlegt sie angeblich, ihren Namen in Blackbock zu ändern. Möglich wäre allerdings auch, dass dies alles nur erfunden ist.
Mehr Satirisches und Ernstes: www.thomas-eisinger.de
-
 @ 6ad3e2a3:c90b7740
2025-04-23 12:31:54
@ 6ad3e2a3:c90b7740
2025-04-23 12:31:54There’s an annoying trend on Twitter wherein the algorithm feeds you a lot of threads like “five keys to gaining wealth” or “10 mistakes to avoid in relationships” that list a bunch of hacks for some ostensibly desirable state of affairs which for you is presumably lacking. It’s not that the hacks are wrong per se, more that the medium is the message. Reading threads about hacks on social media is almost surely not the path toward whatever is promised by them.
. . .
I’ve tried a lot of health supplements over the years. These days creatine is trendy, and of course Vitamin D (which I still take.) I don’t know if this is helping me, though it surely helps me pass my blood tests with robust levels. The more I learn about health and nutrition, the less I’m sure of anything beyond a few basics. Yes, replacing processed food with real food, moving your body and getting some sun are almost certainly good, but it’s harder to know how particular interventions affect me.
Maybe some of them work in the short term then lose their effect, Maybe some work better for particular phenotypes, but not for mine. Maybe my timing in the day is off, or I’m not combining them correctly for my lifestyle and circumstances. The body is a complex system, and complex systems are characterized by having unpredictable outputs given changes to initial conditions (inputs).
. . .
I started getting into Padel recently — a mini-tennis-like game where you can hit the ball off the back walls. I’d much rather chase a ball around for exercise than run or work out, and there’s a social aspect I enjoy. (By “social aspect”, I don’t really mean getting to know the people with whom I’m playing, but just the incidental interactions you get during the game, joking about it, for example, when you nearly impale someone at the net with a hard forehand.)
A few months ago, I was playing with some friends, and I was a little off. It’s embarrassing to play poorly at a sport, especially when (as is always the case in Padel) you have a doubles partner you’re letting down. Normally I’d be excoriating myself for my poor play, coaching myself to bend my knees more, not go for winners so much. But that day, I was tired — for some reason I hadn’t slept well — and I didn’t have the energy for much internal monologue. I just mishit a few balls, felt stupid about it and kept playing.
After a few games, my fortunes reversed. I was hitting the ball cleanly, smashing winners, rarely making errors. My partner and I started winning games and then sets. I was enjoying myself. In the midst of it I remember hitting an easy ball into the net and reflexively wanting to self-coach again. I wondered, “What tips did I give to right the ship when I had been playing poorly at the outset?” I racked my brain as I waited for the serve and realized, to my surprise, there had been none. The turnaround in my play was not due to self-coaching but its absence. I had started playing better because my mind had finally shut the fuck up for once.
Now when I’m not playing well, I resist, to the extent I’m capable, the urge to meddle. I intend to be more mind-less. Not so much telling the interior coach to shut up but not buying into the premise there is a problem to be solved at all. The coach isn’t just ignored, he’s fired. And he’s not just fired, his role was obsoleted.
You blew the point, you’re embarrassed about it and there’s nothing that needs to be done about it. Or that you started coaching yourself like a fool and made things worse. No matter how much you are doing the wrong thing nothing needs to be done about any of it whatsoever. There is always another ball coming across the net that needs to be struck until the game is over.
. . .
Most of the hacks, habits and heuristics we pick up to manage our lives only serve as yet more inputs in unfathomably complex systems whose outputs rarely track as we’d like. There are some basic ones that are now obvious to everyone like not injecting yourself with heroin (or mRNA boosters), but for the most part we just create more baggage for ourselves which justifies ever more hacks. It’s like taking medication for one problem that causes side effects, and then you need another medicine for that side effect, rinse and repeat, ad infinitum.
But this process can be reverse-engineered too. For every heuristic you drop, the problem it was put into place to solve re-emerges and has a chance to be observed. Observing won’t solve it, it’ll just bring it into the fold, give the complex system of which it is a part a chance to achieve an equilibrium with respect to it on its own.
You might still be embarrassed when you mishit the ball, but embarrassment is not a problem. And if embarrassment is not a problem, then mishitting a ball isn’t that bad. And if mishitting a ball isn’t that bad, then maybe you’re not worrying about what happens if you botch the next shot, instead fixing your attention on the ball. And so you disappear a little bit into the game, and it’s more fun as a result.
I honestly wish there were a hack for this — being more mindless — but I don’t know of any. And in any event, hack Substacks won’t get you any farther than hack Twitter threads.
-
 @ df478568:2a951e67
2025-04-22 18:56:38
@ df478568:2a951e67
2025-04-22 18:56:38"It might make sense just to get some in case it catches on. If enough people think the same way, that becomes a self fulfilling prophecy. Once it gets bootstrapped, there are so many applications if you could effortlessly pay a few cents to a website as easily as dropping coins in a vending machine." --Satoshi Nakamoto The Cryptography Mailing List--January 17, 2009
Forgot to add the good part about micropayments. While I don't think Bitcoin is practical for smaller micropayments right now, it will eventually be as storage and bandwidth costs continue to fall. If Bitcoin catches on on a big scale, it may already be the case by that time. Another way they can become more practical is if I implement client-only mode and the number of network nodes consolidates into a smaller number of professional server farms. Whatever size micropayments you need will eventually be practical. I think in 5 or 10 years, the bandwidth and storage will seem trivial. --Satoshi Nakamoto Bitcoin Talk-- August 5, 2010
I very be coded some HTML buttons using Claude and uploaded it to https://github.com/GhostZaps/ It's just a button that links to zapper.fun.
I signed up for Substack to build an email address, but learned adding different payment options to Substack is against their terms and services. Since I write about nostr, these terms seem as silly as someone saying Craig Wright is Satoshi. It's easy to build an audience on Substack however, or so I thought. Why is it easier to build an audience on Subtack though? Because Substack is a platform that markets to writers. Anyone with a ~~pen~~ ~~keyboard~~ smartphone and an email can create an account with Substack. There's just one problem: You are an Internet serf, working the land for your Internet landlord--The Duke of Substack.
Then I saw that Shawn posted about Substack's UX.
I should have grabbed my reading glasses before pushing the post button, but it occurred to me that I could use Ghost to do this and there is probably a way to hack it to accept bitcoin payments over the lightning network and host it yourself. So I spun my noddle, doodled some plans...And then it hit me. Ghost allows for markdown and HTML. I learned HTML and CSS with free-code camp, but ain't nobody got time to type CSS so I vibe-coded a button that ~~baits~~ sends the clicker to my zapper.fun page. This can be used on any blog that allows you to paste html into it so I added it to my Ghost blog self-hosted on a Start 9. The blog is on TOR at http://p66dxywd2xpyyrdfxwilqcxmchmfw2ixmn2vm74q3atf22du7qmkihyd.onion/, but most people around me have been conditioned to fear the dark web so I used the cloudflared to host my newsletter on the clear net at https://marc26z.com/
Integrating Nostr Into My Self-Hosted Ghost Newsletter
I would venture to say I am more technical than the average person and I know HTML, but my CSS is fuzzy. I also know how to print("Hello world!") in python, but I an NPC beyond the basics. Nevertheless, I found that I know enough to make a button. I can't code well enough to create my own nostr long-form client and create plugins for ghost that send lightning payments to lighting channel, but I know enough about nostr to know that I don't need to. That's why nostr is so F@#%-ing cool! It's all connected. ** - One button takes you to zapper.fun where you can zap anywhere between 1 and ,000,000 sats.** - Another button sends you to a zap planner pre-set to send 5,000 sats to the author per month using nostr. - Yet another button sends you to a zap planner preset to send 2,500 sats per month.
The possibilities are endless. I entered a link that takes the clicker to my Shopstr Merch Store. The point is to write as self-sovereign as possible. I might need to change my lightning address when stuff breaks every now and then, but I like the idea of busking for sats by writing on the Internet using the Value 4 Value model. I dislike ads, but I also want people to buy stuff from people I do business with because I want to promote using bitcoin as peer-to-peer electronic cash, not NGU porn. I'm not prude. I enjoy looking at the price displayed on my BlockClock micro every now and then, but I am not an NGU porn addict.
This line made this pattern, that line made this pattern. All that Bolinger Bart Simpson bullshit has nothing to with bitcoin, a peer-to-peer electronic cash system. It is the musings of a population trapped in the fiat mind-set. Bitcoin is permissionless so I realized I was bieng a hipocryte by using a permissioned payment system becaue it was easier than writing a little vibe code. I don't need permission to write for sats. I don't need to give my bank account number to Substack. I don't need to pay a 10$ vig to publish on a a platform which is not designed for stacking sats. I can write on Ghost and integrate clients that already exist in the multi-nostr-verse.
Nostr Payment Buttons
The buttons can be fouund at https://github.com/Marc26z/GhostZapButton
You can use them yourself. Just replace my npub with your npub or add any other link you want. It doesn't technically need to be a nostr link. It can be anything. I have a link to another Ghost article with other buttons that lead down different sat pledging amounts. It's early. Everyone who spends bitcoin is on nostr and nostr is small, but growing community. I want to be part of this community. I want to find other writers on nostr and stay away from Substack.
Here's what it looks like on Ghost: https://marc26z.com/zaps-on-ghost/
npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0
-
 @ cb4352cd:a16422d7
2025-04-29 11:02:13
@ cb4352cd:a16422d7
2025-04-29 11:02:13As new technologies reshape finance, the traditional banking model faces fresh competition. Let's take a closer look at how the two ecosystems compare today.
What happens when centralized institutions meet decentralized protocols? A transformation of financial services is already underway — and users are at the center of it.
Traditional Banking: Established, Yet Rigid
Traditional banks like JPMorgan Chase, HSBC, and Deutsche Bank have built vast infrastructures over decades. They offer deposit insurance, personal loans, mortgages, and extensive regulatory compliance. Trust, scale, and government support are their major strengths.
However, these institutions often struggle with agility. Opening an international account or sending a cross-border payment can take days and involve considerable fees. Innovations like digital onboarding and instant payments are arriving slowly, hampered by regulatory complexity and legacy systems.
DeFi Platforms: Agile, Accessible, but Risky
By contrast, DeFi protocols such as Uniswap (decentralized exchange), Aave (decentralized lending), and Compound (decentralized borrowing) offer near-instant services, accessible globally 24/7.
DeFi users maintain custody of their own assets. No bank approvals, no office hours. Fees are often lower, and yields can be attractive. Smart contracts automatically execute transactions, removing human bottlenecks.
But DeFi isn't without risks. Without insurance, users are exposed to smart contract bugs, hacks, and protocol failures. Regulatory protections are minimal, and scams can proliferate among unverified projects.
The Bridge Between Worlds: Emerging Hybrids
Interestingly, some traditional players are exploring DeFi-like services. Societe Generale issued tokenized bonds on Ethereum. ING is researching zero-knowledge proofs for financial privacy. Meanwhile, crypto-friendly banks like Silvergate have pioneered instant settlement networks inspired by blockchain efficiency.
The future may not be a winner-takes-all scenario but a convergence: decentralized technology improving traditional services, while banks offer compliant, user-friendly access to digital assets.
Beyond Banking Conference by WeFi: Charting the Future
The ongoing fusion of DeFi and traditional finance will take center stage at the upcoming Beyond Banking Conference by WeFi. Thought leaders and innovators will explore how transparency, smart contracts, and decentralized trust models are redefining global finance.
As these worlds collide, the real question isn't about winners — it's about how finance can evolve to serve a broader, more connected world.
-
 @ f1f59549:f4121cfe
2025-04-28 20:37:37
@ f1f59549:f4121cfe
2025-04-28 20:37:37I've been fascinated with the concept of existential uncertainty lately.
Claudio Naranjo, inventor of the Enneagram, calls it the "ontic void" — a loss of clear awareness of the nature of one's own being.
The Japanese have a term for this, too. Mumyo means obscurity, lack of clarity, or an absence of clear awareness.
Psychology textbooks call it a "disruption of fundamental axioms."
Whatever you want to call it, the progression into full-fledged ontological shock is the same.
Ontological shock happens when our foundational beliefs about who we are and our place within the universe unravel, leaving us exposed to the void. It's a dizzying and disorienting experience, but ultimately an important catalyst for profound growth and understanding.
It all starts with the ego.
The ego creates a picture of reality that conforms with one's lived experiences.
I know that I am "me," and You are "you." I know that objects and people exist independently of me and that time flows in a linear direction.
Simple stuff.
Zen Buddhism points out that the picture our ego creates for us is an illusion. Mayoi refers to the state of being lost in the illusions and attachments of the world, which obscures the true nature of existence and the self.
Psychologists believe this fabricated reality the ego crafts for us serves an important purpose. It helps cut the noise and allows us to exist in a world infinitely more complex than our human minds could possibly comprehend.
The practice of meditation is intended to help cut through this illusion to awaken us from the dream of ordinary perception and guide us into the realization of emptiness (Sunyata) and the interconnectedness of all things.
This is the path to enlightenment according to the Zen Buddhist tradition.
All of this sounds great on paper, but the process of uncovering illusion is inherently painful. It demands a steady flow of existential uncertainty to creep into our awareness. Sometimes it comes flowing in faster than we can cope with.
Near-death experiences, diagnosis with a terminal illness, deep meditation, and strong psychedelic drugs can all shatter the delicate facade imposed by our ego in an instant — leading to radical and polarizing shifts in one's understanding of the universe and our relationship to it.
Any such challenge to one's worldview inundates the mind with a swirling vortex awe and terror.
When the scale is tipped towards awe, the user experiences a state of euphoria and peace. These experiences are more aligned with the idea of Satori (snippets of enlightenment and awakening).
When the scale tips towards terror, the user experiences a state of shock. These experiences are aligned with the idea of spiritual dread and exsistential crisis.
It's not always so straightforward, either. While the void could be glittering at its peak, it could feel like a bottomless pit the morning after.
“Visions More Real Than Real Life”
Of all the psychedelic explorations I’ve had in my life, nothing stands out as having caused a more profound shift in my worldview than an experience I had with salvia about 10 years ago.
It was an experience so bizarre I refused to talk about it for many years. After a while, I started sharing my experience with others and was shocked by how many others had similar stories.
During the trip, I left my body and was sucked into a crushing void. I was scared and tried to escape but was inevitably swallowed by the abyss.
When I came out the other side, reality was like nothing I've ever seen before. It even had different laws of physics. Yet there was something about this strange place that felt even more real than reality itself.
It felt like I had just woke up from a dream — only the dream was my regular reality. My identity, my friends, my family, and all my hopes and aspirations were nothing but a hallucination.
This experience shattered my view of reality and left me with a gnawing feeling of existential uncertainty lasting months after the trip.
What the hell was that? Did I catch a glimpse of the real real world and what I’m living now is merely a vivid dream? Will I “wake up” in that place again after I die? What is the meaning of that terrifying void?
Big questions. No answers.
Up until this point I only had one frame of reference for what it meant to exist. This experience challenged my understanding of reality in a deeply unsettling way.
I kept myself preoccupied with other things. But every once in a while this creeping sensation of the void would linger over my shoulders. It would remind me that there’s more to reality than I could ever understand.
This profound experience changed the way I think about the world and what it means to be conscious it in a big way — but it was far from a unique experience.
A study published in 2020 surveyed people who reported encounters with "entities" after taking DMT. Researchers found that 81% of users reported the experience to feel "more real than reality."
Existence is Deeply Strange
What I've come to realize, many years after this experience, is that the nature of reality is incomprehensible.
There are things going on that we're simply unable to understand.
Exploring the mind through psychedelics or dedicated meditation practice doesn't allow us to understand the "secret sauce" of existence — but they can certainly give us a glimpse of it.
They help us see just enough to realize how absurd our very existence is and how little we truly know about ourselves and the world around us.
Here's where Zen Buddhism comes in.
Zen teaches that the more we try to find answers to the mysteries of existence, the further we get from the answer. The paradox is that we should still try to understand — but with the expectation that we’re going to fail.
Only once the mind has exhausted itself through sincere effort and surrendered completely to failure can we even come close to comprehending the true essence of being.
 # Zen Buddhism, Preparedness, & Ontological Shock
# Zen Buddhism, Preparedness, & Ontological ShockSwiss psychologist Carl Jung was intimately aware of the seriousness of ontological shock, especially in the context of psychedelics.
He left us with an ominous warning to "beware of unearned wisdom."
What Jung was suggesting was that if you don't do the leg work and learn to swim before jumping into the deep end of the pool — you shouldn't be surprised if you can't handle where you end up.
Taking strong psychedelics like DMT, ayahuasca, salvia, psilocybin, or LSD is like jumping into the deep end of the existential pool.
People who have taken the steps to question their existence beforehand are more likely to ride the wave of awe rather than succumb to the depths of terror and delusion.
In Zen Buddhism, the practice of mindfulness and meditation is encouraged as a means to prepare oneself for whatever reality exists beyond the ego's construction. The lesson is that we must face the void with equanimity and without attachment. Clinging to the experience, to our version of reality, or to expectations of any kind leads to turmoil, terror, and ontological suffering.
As Tibetan Buddhist Master, Dudjom Rinpoche, once said:
"If you see anything horrible, don't cling to it; if you see anything beautiful, don't cling to it."
Zen Koans
Here’s a collection of Zen koans relate to the ontic void, ontological shock, and the radical shift in worldview.
Subscribe to The Zen Psychedelic
Thanks for reading The Zen Psychedelic! Consider subscribing for free to receive new posts and support my work.
You can subscribe here using Nostr or follow me on Substack.
→ This post was originally published on The Zen Psychedelic Substack
-
 @ f1f59549:f4121cfe
2025-04-28 20:34:50
@ f1f59549:f4121cfe
2025-04-28 20:34:50When the world feels like it's falling apart, we often look for a beacon of hope — someone to lead us through the darkness. But what if those in charge are more concerned with their own agendas than with the well-being of the people they serve?
History teaches us that power, no matter how well-intentioned, has a tendency to corrupt and that even the most selfless vision can be dismantled by ego.
This corruption not only undermines society but also seeps into our individual lives — contributing to a sense of helplessness, frustration, and suffering.
Amidst the growing storm of instability, Zen Buddhism provides us with the wisdom to navigate turbulent times with clarity, composure, and resilience.
Here are three Zen principles that help us stay grounded, clear-headed, and resilient in the face of the coming storm.
1. Cultivate Total Awareness
“All warfare is based on deception.” — Sun Tzu
While Zen may encourage us to avoid clinging to identities, outcomes, and material possessions, it certainly does not call for passivity and escapism. Zen is about cultivating a state of total awareness that fosters meaningful and intentional engagement with the world around us.
Even the process of cultivating awareness itself is not a passive act; it requires great effort — but failing to do so inevitably leads to confusion and suffering.
In today's growing digital oligarchy, our attention has become a commodity to be ensnared and exploited. Social media companies, news outlets, and the powerful elite have mastered the art of distraction and control.
When we surrender to distraction and mindlessness, our awareness gives way to complacency. Our thoughts and desires are drowned in noise, and our ability to confront challenges with clarity becomes clouded by the poison of ignorance and inaction.
Cultivating total awareness through mindful action in all areas of life is the antidote that allows us to reclaim control over our minds and actions and resist the pull of ignorance.
We must avoid the trap of mindlessness — resist the doomscroll, avoid the urge to escape through mind-altering substances, reject repressive authority, and refuse to let the chaos and distraction of crisis swallow us whole.
Zen koans on practicing total awareness:
2. Look Beyond Extremes (Embrace Non-Duality)
"Those who are wise do not seek extremes, but find balance in everything." — Confucius
Zen philosophy is deeply centered around the concept of non-duality. This is the idea that all things are interconnected, and the separation between opposites (like good and bad, hope and despair) is an illusion.
It's easy to fall into the trap of seeing the world as divided into polar opposites — we either have societal progress or collapse; hope or despair; success or failure — there are no in-betweens.
One of my favorite Zen koans illustrates this concept perfectly. In this story a wise farmer experiences a series of events that blur the lines between "good events" and "bad events" — each directly feeding into one another.
First, a bad event occurs, and his neighbors give him sympathy for his troubles — but the wise farmer knows that all events are impermanent and interconnected, so he refuses this sympathy.
The following day, as a direct byproduct of the bad event that occurred the day before, something good happens. His neighbors come to congratulate him on his luck — but the wise farmer refuses this praise as well.
This continues back and forth — something good happens that causes something bad to happen, that causes something good to happen until the story ends.
This story exposes the simple truth that life’s events cannot be neatly categorized into good or bad, and we cannot, under any circumstances, predict what future outcomes will result from any given event.
The idea I'm trying to highlight here is that in times of major crisis, it’s easy to become overwhelmed by the immediate "bad" events and to lose sight of the bigger picture. Life’s unpredictability means that each crisis, while painful, may contain within it the seeds of growth or change. Embracing the flow of events without rushing to label them as good or bad helps us stay grounded, clearheaded, and able to respond with composure.
We cannot control the course of a crisis, but we can navigate it more effectively by seeing beyond extremes and understanding that, like the farmer, each moment is part of an ongoing cycle of change.
3. Choose Action Over Sympathy
Compassion (Karuṇā) is a core tenet of Buddhism — but it's not enough to simply feel for others. Zen teaches that compassion requires action. Whether through small acts of kindness or large-scale efforts, compassion is about actively engaging with the world, not just observing it.
The Zen concept of compassion is rooted in non-attachment and equanimity. It arises from the understanding that all beings are interconnected and that our actions should be free from self-interest or ego.
With that said, compassion doesn’t mean being consumed by others' pain. We cannot lose ourselves in it, for doing so only perpetuates the suffering.
In the face of crisis, we must remember — you can’t defeat hate with hate. Only through compassion can we break the cycle of suffering.
Subscribe to The Zen Psychedelic
Thanks for reading The Zen Psychedelic! Consider subscribing for free to receive new posts and support my work.
You can subscribe here using Nostr or follow me on Substack.
→ This post was originally published on The Zen Psychedelic Substack
-
 @ f10512df:c9293bb3
2025-04-22 17:11:05
@ f10512df:c9293bb3
2025-04-22 17:11:05Details
- 🍳 Cook time: 5-7 minutes
- 🍽️ Servings: 1
Ingredients
- 2 eggs
- Shredded cheese (Sharp cheddar is a favorite)
- 1 Tbsp olive oil or ghee
Directions
- Add oil to a non-stick pan and allow it to get hot (med-high heat)
- Add eggs and additional toppings, scramble and wait for the edges to get brown.
- Add shredded cheese while edges are browning. It is best if cheese begins to melt before flipping.
- Flip, and make sure all cheese stayed down, and there is enough oil left in the pan.
- Keep checking until pan side of eggs lift easily. Done correctly, the cheese will form a crisp layer.
- When fully cooked, serve with cheese right side up and enjoy!
-
 @ f1f59549:f4121cfe
2025-04-28 20:31:58
@ f1f59549:f4121cfe
2025-04-28 20:31:58Power despises uncertainty. It craves permanence, hierarchy, and control. The Dark Enlightenment movement is an attempt to grant exactly that — a version of a world where democracy is abandoned, governance is streamlined into autocratic rule, and the messy unpredictability of human freedom is replaced with rigid order and the unshakable rule of anointed elites.
Since the return of the orange man, I’ve been seeing a lot more Dark Enlightenment rhetoric seeping into my news feed. Its influence on political discourse, tech elitism, and reactionary online spaces is becoming more brazen by the day.
So, after spending a stupid amount of time digging into this topic (most of it lost in the labyrinth of Curtis Yarvin’s deliberately opaque writing) — here's a rundown of what the Dark Enlightenment is, why I believe its misaligned ideals serve only to further illusion and suffering, and how it stands in direct contradiction to the Zen perspective on governance, suffering, and the futility of clinging to control.
The Cult of Order & Collapse
The Dark Enlightenment is a neo-reactionary political movement that emerged in Silicon Valley sometime in the early 2010s. It's a movement that rejects democracy, egalitarianism, and classical Enlightenment ideals like individual rights and social progress.
Instead, the Dark Enlightenment embraces authoritarianism, technocapitalism, and genetic determinism.
It suggests that Karl Marx and his followers had the right diagnosis (that capitalism is inherently unstable) — but drew the wrong conclusions, believing its abolition would lead to an egalitarian, classless society. The Dark Enlightenment, by contrast, sees capitalism’s chaos as inevitable and argues that order can only be restored through strict hierarchy and authoritarian rule.
While other traditional leftists (such as social democrats) try to control capitalism through government intervention and social welfare programs to limit its harms on humanity, the Dark Enlightenment embraces this harm. It suggests that the inevitable crash and burn will have a net positive impact on society by forcing its collapse and allowing us to create something radically new from the rubble.
This acceleration of capitalism will exacerbate suffering until it reaches a breaking point — at which point a new order ruled by a technological elite will emerge.
The idea is that in order for things to get better, they need to get a lot, LOT worse.
The Dark Enlightenment movement is largely based on the ideas of Nick Land — a former professor and philosopher at the University of Warwick. Land is known for his provocative and nihilistic views on capitalism and technology.
Land is also the founder of accelerationist theory, a closely related topic we'll explore next that involves pushing technological advancement to the extreme to reach a "singularity" — regardless of its risk to society.
Accelerationism
“The more you grasp, the less you hold.” — Old Zen Proverb.
Accelerationism is a response to the perceived stagnation or decline of society and the belief that only radical change can overcome it. It's the idea that pushing capitalism and technology to their limits will either create a singularity that transforms society or force a necessary collapse and rebirth.
While some might argue that accelerationism could be a maneuver to maximize actions taken that provide the greatest overall good for humanity, rather than prioritizing personal interest, this idealized version rarely plays out in reality.
Accelerationism has become an excuse to justify reckless progress without consideration for the harm caused along the way.
I see accelerationism as a modern form of samsara — it's an endless, insatiable cycle of craving and dissatisfaction. At what point will we reach the desired state of advancement and decide, "Hey, we did it. Now let's all just quit our jobs, kick back with a cold beer, and enjoy our utopia!"
The very nature of accelerationism is to crave and push for more and more without end.
Even if the end goal of such a movement is some sort of "perfect society" wherein all members are treated fairly and equally — have access to healthy food, personalized education, free healthcare, housing, and opportunity — it's based entirely on illusion and ultimately relies on the perpetuation, even acceleration, of suffering to sustain itself.
From a Zen perspective, the path forward is not to obsess about advancement and accelerate progress at all costs — but to strive for a steady, effortless flow with the natural rhythm of change and existence.
Technocapitalism & The Loss of the Self
“It’s not that we’ve lost control of our data. It’s that we’ve lost control of ourselves.” — Shoshana Zuboff
A truly capitalistic system reduces the individual to a cog in a machine. Under technocapitalism, the self becomes less important than the system it operates within. Our individuality, emotions, and autonomy are all set aside to serve the greater mechanism of the market.
In Zen, this loss of individuality is not inherently negative — it resonates with the idea that we are all part of an interconnected whole. However, where Zen teaches that liberation arises through the mindful dissolution of the ego, technocapitalism co-opts this loss of self for its own ends.
The self is not something to be manipulated and exploited by external forces. True freedom lies in non-attachment to any system — capitalist, technocratic, or otherwise.
The CEO State
“Govern a great nation as you would cook a small fish. Do not overdo it.” — Lao Tzu
One of the core ideas of the Dark Enlightenment movement is that democracy is both inefficient and chaotic. Instead, followers promote the emergence of an authoritarian "CEO state" — in which governance is centralized under a technocratic elite.
Curtis Yarvin even imagines a transition toward corporate-style city-states, in which each polity is ruled by a sovereign CEO who maintains total authoritarian rule. Citizens would have the freedom to decide which city-state best aligns with their ideals. If a leader fails, the "customers" (citizens) can leave — but they have no say in shaping policy. He even goes as far as to suggest that the now-decimated city of Gaza should be the first location for these new monarchical city-states.
The whole concept of the CEO state contradicts the Zen understanding that true freedom arises when we let go of attachment to form. Freedom is not something that can be granted or taken by external systems — it’s an internal liberation state achieved through non-attachment and non-striving.
Utopia: The Trap of Endless Striving
“The finger pointing at the moon is not the moon.” — Zen Proverb
Not all forms of accelerationism embrace collapse and control.
For example, left accelerationism — as championed by thinkers like Sam Altman, Aaron Bastani, Nick Srnicek, and Alex Williams — envisions a future where technology serves human freedom and well-being. Rather than racing toward authoritarianism and the collapse of society, it seeks to accelerate progress to expand human flourishing. This is achieved (in theory) by using automation to reduce working hours (thus providing us with more leisure time), implementing universal basic income (for greater financial security), and improving healthcare, education, and housing for all.
The goal of left accelerationism is to free people from unnecessary toil and scarcity by harnessing technology to create a more equitable society for all. It’s a vision of abundance rather than dominance, aiming for liberation from the economic structures that constrain human potential.
However, even this optimistic vision is a trap. The idea of a perfect society — a technological utopia — remains just that: an illusion. From a Zen perspective, striving for utopia — whether through technological liberation or authoritarian control — is rooted in attachment, desire, and illusion.
No matter how noble the goal, acceleration driven by fear and craving only deepens suffering. True freedom lies not in speeding toward some imagined perfect society, but in learning to live in the present moment, unattached to outcomes or illusions of control.
To believe that suffering can be eliminated through progress alone is to misunderstand the nature of suffering itself. As long as we seek to escape the present by chasing an imagined future, we remain trapped — no matter how advanced or automated the world around us becomes.
Fear, Control, & The Search For True Freedom
“We are very afraid of being powerless. But we have the power to look deeply at our fears, and then fear cannot control us.” — Thich Nhat Hanh
The Dark Enlightenment is a manifestation of fear — fear of chaos, fear of loss, and fear of weakness.
Its response is to control, subjugate, dominate, and push the acceleration of technology beyond the point of no return — driving society toward total collapse.
Even if the intent is altruistic — that an even greater, more equitable society will emerge from the ashes — this belief rests on an illusion. Destruction does not guarantee rebirth, and control does not guarantee liberation.
Depending on where your perspective stands, some of this could be seen as either altruistic or reckless — but from a Zen perspective, this whole approach is missing the mark entirely. The harder we push to force change, the more tangled we become in the very suffering we seek to escape.
We break free not by forcing change — but by letting go and moving with the flow.
Subscribe to The Zen Psychedelic
Thanks for reading The Zen Psychedelic! Consider subscribing for free to receive new posts and support my work.
You can subscribe here using Nostr or follow me on Substack.
→ This post was originally published on The Zen Psychedelic Substack
-
 @ 7e538978:a5987ab6
2025-04-29 09:57:21
@ 7e538978:a5987ab6
2025-04-29 09:57:21In Jericoacoara, Brazil, a beach town famed for its natural beauty and vibrant tourism, an innovative project is reshaping how locals and visitors think about money. Praia Bitcoin is an ambitious initiative to build a circular economy powered entirely by Bitcoin.
Launched in 2021 by entrepreneur Fernando Motolese, Praia Bitcoin was inspired by the Bitcoin Beach project in El Zonte, El Salvador. The vision is simple: create a self-sustaining Bitcoin economy where businesses and individuals use Bitcoin everyday in place of fiat money.
This idea holds special significance in Jericoacoara, where traditional banking services are scarce. The town lacks even basic infrastructure like ATMs, making financial inclusion a pressing need. With Praia Bitcoin, Bitcoin isn’t just a store of value—it’s a tool to empower a community and connect it to the global economy.
Transforming Jericoacoara with Bitcoin
Since its inception, Praia Bitcoin has worked to foster Bitcoin adoption in the area. Starting with a modest donation of 0.02 BTC, Fernando and his team have built a thriving ecosystem:
- Over 40 businesses now accept Bitcoin, ranging from souvenir shops and tour operators to beach vendors.
- Local students have received Bitcoin-loaded tap-to-pay, Bolt Cards, to use in their daily lives.
- Creative initiatives like “Bitcoin Banana Day” or "Frutas por Sats" (fruits for sats) where children buy fruits for 10 satoshis at school, have brought global attention to the project.
Praia Bitcoin’s success isn’t just about the adoption numbers, it’s about the stories. Families use Bitcoin to shop, business owners save on transaction fees, and children are learning the value of sound money at an early age.
LNbits - The Technology Behind Praia Bitcoin
Creating an economy on Bitcoin’s Lightning Network requires more than enthusiasm, it needs robust tools that are easy to use and adaptable to local needs. That’s where LNbits comes in.
Fernando and the Praia Bitcoin team have used LNbits’ open-source software to solve practical challenges and scale the project. With its modular design, LNbits provides tools that allow Praia Bitcoin to:
- Set Up Wallets: Community members receive user-friendly wallets that connect seamlessly to the Lightning Network, enabling fast, low-cost transactions.
- Issue BoltCards: Using LNbits’ BoltCard extension, the team has distributed NFC-enabled cards, allowing tap-to-pay functionality that makes Bitcoin payments as simple as using a credit card.
- Enable Flexible Payments: The project utilizes LNbits’ Point of Sale TPoS extension that allows merchants to easily receive Lightning Network payments.
Breaking Records, Building Community
Fernando doesn’t just implement solutions, he pushes boundaries. One of his most remarkable achievements was an attempt to set a world record for the most Lightning Network payments in the shortest amount of time. Over the course of one afternoon, 100 children in Jericoacoara received payments of 21,000 satoshis each, demonstrating the scalability and speed of Lightning-powered transactions.
This wasn’t just a technical feat, it was a community moment. The event showed how Bitcoin could serve as a tool for engagement, education, and empowerment, all while highlighting the possibilities of using the Lightning Network for real-world applications.
A Collaborative Approach to Innovation
One of the unique strengths of LNbits is its ability to evolve based on community feedback. While Fernando Motolese and Praia Bitcoin operate independently, their insights have helped refine the LNbits platform.
For example, Fernando’s need for a PIN-less ATM functionality led the LNbits team to implement that feature in the TPoS extension, that had the functionality but required a security PIN. This kind of collaboration isn’t about formal partnerships. It’s about how an open-source ecosystem thrives when real-world needs drive innovation.
The feedback loop between users like Fernando and developers ensures LNbits remains practical and relevant—not just for Praia Bitcoin but for countless other projects worldwide.
The Ripple Effect of Praia Bitcoin
Praia Bitcoin is a case study in what’s possible when Bitcoin meets a strong vision. By leveraging Bitcoin, the Lightning Network and LNbits, the project has redefined financial access in Jericoacoara, proving that small communities can lead big innovations.
For LNbits, Praia Bitcoin showcases the value of adaptable, open-source solutions. Whether it’s creating wallets, enabling NFC payments, or refining tools for real-world use, LNbits provides the infrastructure that makes projects like Praia Bitcoin possible.
But beyond the technical achievements, Praia Bitcoin reminds us of the human impact of Bitcoin adoption. It’s about children buying their first bananas with satoshis, families running businesses with lower fees, and a community connecting to a global financial network for the first time.
Conclusion
Praia Bitcoin’s journey is only getting started and its success is inspiring similar initiatives worldwide. For LNbits, being part of this story, is a testament to the power of the software and of open-source collaboration.
If you’re ready to build the future of Bitcoin adoption, LNbits offers the tools to turn ideas into impact.
Learn More:
- Visit Praia Bitcoin: Praia Bitcoin
- Explore LNbits: LNbits -
 @ f10512df:c9293bb3
2025-04-22 17:00:44
@ f10512df:c9293bb3
2025-04-22 17:00:44Chef's notes
Use a tea bag to hold the spices. I like to fill it and drape it on the side of the pan so the flavors get in, and then toss it before serving. Easier than picking rosemary out of your teeth later.
Details
- ⏲️ Prep time: 20 minutes
- 🍳 Cook time: 1 hour 45 from scratch, 45 if using chicken stock
- 🍽️ Servings: 4
Ingredients
- 1 Cup Carrots (sliced)
- 1C celery (sliced)
- 2 cloves garlic
- 1 tsp dried thyme
- 1/2 tsp dried minced onion
- 2 Tbsp lemon juice (or more to taste)
- 1/2 Tbsp salt (to taste)
- 1 rotisserie chicken
- 2 tsp dried rosemary (or 1-2 sprigs fresh)
- 8 C water & additional 1-2 C later
- 10 oz pre-cooked noodles
- 1 tsp cracked pepper (to taste)
Directions
- Remove chicken meat from bones and set aside. Do not discard skin. Put bones and skin in a large stock pot and add water. Let boil covered for one hour, and then remove bones and strain out any bits of skin from broth.
- Add chopped vegetables, spices, and lemon juice to broth with up to 2 C. additional water to replace what might have boiled away. Simmer over low to medium heat (covered) for another half hour, stirring occasionally. Add in chicken meat. Taste test and add additional salt if needed.
- When vegetables are cooked, add in noodles and stir for an additional 2-3 minutes until hot (uncovered), and enjoy.
- If using store bought chicken stock, only simmer until vegetables are cooked (about half an hour).
-
 @ a4043831:3b64ac02
2025-04-29 09:19:05
@ a4043831:3b64ac02
2025-04-29 09:19:05A professional financial advisor can guide you to achieve long-term financial stability. They can assist you to define your goals to formulate strategic planning coupled with rational decision-making. Since the options are varied and multiple, how can you go about choosing a fiduciary financial advisor whose approach matches their financial goals? This guide explains exactly how to pick a financial advisor who suits your individual financial targets.
Defining Your Financial Needs and Goals
You need to specify your financial aspirations as well as your essential requirements so an advisor can create a suitable plan for your portfolio. Starters should establish their monetary targets before initiating contact with financial consultants. Any objective requires planning such as retirement preparation and investment management and education savings along with wealth protection and growth needs to be identified. Knowing your financial goals helps you determine if an advisor’s experience matches the needs of reaching your targets. Before you conduct meetings with possible financial advisors you need to have clearly established financial goals which will make these meetings goal-focused and beneficial.
Trusted financial advisors at Passive Capital Management can help you check out financial plan tailored to your needs and goals.
Look For Professional Credentials and Qualifications
Review carefully the advisor’s qualifications after you establish your goals. The strict training and ethical assessments that CFP Certified Financial Planner and the CFA Chartered Financial Analyst professionals demonstrate their professionalism. The designations set by these organizations prove advisors maintain knowledge in planning, investments and regulatory requirements. It is essential to verify that the advisor operates under fiduciary standards since this legal requirement ensures they must always act according to your benefit. It is essential to verify if an advisor functions as a fiduciary all the time because some only act under specified circumstances. Get a direct and unambiguous statement about their status. Under fiduciary relationships your financial security stands as the main priority of your financial advisor while fiduciary arrangements reduce potential conflicts between your interests.
Understand the Advisor’s Investment Approach
While consulting an advisor, you might encounter several hidden conflicts of interest. So a robust advisor-client connection based on their mutual investment approach including strategy selection is essential. Review the risk approaches of your advisor through inquiries to learn about their portfolio design strategies and market investment strategies. Technical competence must be combined with an awareness of your risk tolerance and time preferences according to their responses. A reliable advisor will adapt their investment methods to match the risk tolerance of their client combined with their financial destination.
Review their Service Package and Communication Style
A competent financial advisor functions past standard investment management duties. Their service range needs to include full-scale financial planning in areas such as retirement income strategies along with tax and estate planning solutions and insurance assessments. Check that their service suite matches your financial development needs. The advisor needs to maintain both clear and predictable ways of communication. Reveal their review process schedule and disclosure methods for reporting metrics as well as their availability to respond to questions at any time during the year. Professional communication builds reliable relationships that involve active participant commitment in planning activities.
Clarify the Fee Structure
Knowing how your advisor gets paid gives you the essential knowledge needed for building trust between you both. Financial advisors conduct business through payment structures which include flat fees, percentage-based fees on managed assets and extra earnings from their advisory products. The different compensation models bring their own effects and outcomes to the process. The most significant aspect for you is receiving clear explanations about fees while they are in alignment with your financial planning. The first practice of transparent communication by an advisor suggests they will uphold that approach during your entire time together.
Conclusion
Alongside numerical expertise your ideal advisor should function as a trustworthy partner because they will dedicate themselves to your financial growth. Strategic decision-making depends on the establishment of clear objectives and verification of expertise as well as confirmation of fiduciary principles and comprehensive evaluation of communication methods and associated fees. Your financial destiny requires organized assessment along with expert consulting while the correct professional consultant enables you to move through every phase of your path with obvious direction and solid self-assurance.
-
 @ a39d19ec:3d88f61e
2025-04-22 12:44:42
@ a39d19ec:3d88f61e
2025-04-22 12:44:42Die Debatte um Migration, Grenzsicherung und Abschiebungen wird in Deutschland meist emotional geführt. Wer fordert, dass illegale Einwanderer abgeschoben werden, sieht sich nicht selten dem Vorwurf des Rassismus ausgesetzt. Doch dieser Vorwurf ist nicht nur sachlich unbegründet, sondern verkehrt die Realität ins Gegenteil: Tatsächlich sind es gerade diejenigen, die hinter jeder Forderung nach Rechtssicherheit eine rassistische Motivation vermuten, die selbst in erster Linie nach Hautfarbe, Herkunft oder Nationalität urteilen.
Das Recht steht über Emotionen
Deutschland ist ein Rechtsstaat. Das bedeutet, dass Regeln nicht nach Bauchgefühl oder politischer Stimmungslage ausgelegt werden können, sondern auf klaren gesetzlichen Grundlagen beruhen müssen. Einer dieser Grundsätze ist in Artikel 16a des Grundgesetzes verankert. Dort heißt es:
„Auf Absatz 1 [Asylrecht] kann sich nicht berufen, wer aus einem Mitgliedstaat der Europäischen Gemeinschaften oder aus einem anderen Drittstaat einreist, in dem die Anwendung des Abkommens über die Rechtsstellung der Flüchtlinge und der Europäischen Menschenrechtskonvention sichergestellt ist.“
Das bedeutet, dass jeder, der über sichere Drittstaaten nach Deutschland einreist, keinen Anspruch auf Asyl hat. Wer dennoch bleibt, hält sich illegal im Land auf und unterliegt den geltenden Regelungen zur Rückführung. Die Forderung nach Abschiebungen ist daher nichts anderes als die Forderung nach der Einhaltung von Recht und Gesetz.
Die Umkehrung des Rassismusbegriffs
Wer einerseits behauptet, dass das deutsche Asyl- und Aufenthaltsrecht strikt durchgesetzt werden soll, und andererseits nicht nach Herkunft oder Hautfarbe unterscheidet, handelt wertneutral. Diejenigen jedoch, die in einer solchen Forderung nach Rechtsstaatlichkeit einen rassistischen Unterton sehen, projizieren ihre eigenen Denkmuster auf andere: Sie unterstellen, dass die Debatte ausschließlich entlang ethnischer, rassistischer oder nationaler Kriterien geführt wird – und genau das ist eine rassistische Denkweise.
Jemand, der illegale Einwanderung kritisiert, tut dies nicht, weil ihn die Herkunft der Menschen interessiert, sondern weil er den Rechtsstaat respektiert. Hingegen erkennt jemand, der hinter dieser Kritik Rassismus wittert, offenbar in erster Linie die „Rasse“ oder Herkunft der betreffenden Personen und reduziert sie darauf.
Finanzielle Belastung statt ideologischer Debatte
Neben der rechtlichen gibt es auch eine ökonomische Komponente. Der deutsche Wohlfahrtsstaat basiert auf einem Solidarprinzip: Die Bürger zahlen in das System ein, um sich gegenseitig in schwierigen Zeiten zu unterstützen. Dieser Wohlstand wurde über Generationen hinweg von denjenigen erarbeitet, die hier seit langem leben. Die Priorität liegt daher darauf, die vorhandenen Mittel zuerst unter denjenigen zu verteilen, die durch Steuern, Sozialabgaben und Arbeit zum Erhalt dieses Systems beitragen – nicht unter denen, die sich durch illegale Einreise und fehlende wirtschaftliche Eigenleistung in das System begeben.
Das ist keine ideologische Frage, sondern eine rein wirtschaftliche Abwägung. Ein Sozialsystem kann nur dann nachhaltig funktionieren, wenn es nicht unbegrenzt belastet wird. Würde Deutschland keine klaren Regeln zur Einwanderung und Abschiebung haben, würde dies unweigerlich zur Überlastung des Sozialstaates führen – mit negativen Konsequenzen für alle.
Sozialpatriotismus
Ein weiterer wichtiger Aspekt ist der Schutz der Arbeitsleistung jener Generationen, die Deutschland nach dem Zweiten Weltkrieg mühsam wieder aufgebaut haben. Während oft betont wird, dass die Deutschen moralisch kein Erbe aus der Zeit vor 1945 beanspruchen dürfen – außer der Verantwortung für den Holocaust –, ist es umso bedeutsamer, das neue Erbe nach 1945 zu respektieren, das auf Fleiß, Disziplin und harter Arbeit beruht. Der Wiederaufbau war eine kollektive Leistung deutscher Menschen, deren Früchte nicht bedenkenlos verteilt werden dürfen, sondern vorrangig denjenigen zugutekommen sollten, die dieses Fundament mitgeschaffen oder es über Generationen mitgetragen haben.
Rechtstaatlichkeit ist nicht verhandelbar
Wer sich für eine konsequente Abschiebepraxis ausspricht, tut dies nicht aus rassistischen Motiven, sondern aus Respekt vor der Rechtsstaatlichkeit und den wirtschaftlichen Grundlagen des Landes. Der Vorwurf des Rassismus in diesem Kontext ist daher nicht nur falsch, sondern entlarvt eine selektive Wahrnehmung nach rassistischen Merkmalen bei denjenigen, die ihn erheben.
-
 @ c1157704:6423de51
2025-04-29 08:54:13
@ c1157704:6423de51
2025-04-29 08:54:13English: "Politicians steal billions and get light sentences, while the poor get jailed for stealing bread. Is the law just a tool for the rich?"
-
 @ f1f59549:f4121cfe
2025-04-28 20:29:19
@ f1f59549:f4121cfe
2025-04-28 20:29:19In a culture that glorifies more — more stuff, more hustle, more optimization — there’s a quiet rebellion in doing less. Not out of laziness, but out of clarity.
The Japanese call it kansō (pronounced kahn-soh).
Kansō means simplicity — the stripping away of ornamentation and unburdening of excess. It’s the art of removing what’s unnecessary so that what is can speak more clearly. It's about being less for the purpose of experiencing more.
This isn’t minimalism co-opted for aesthetic points. It’s a form of spiritual technology. A reminder that true clarity doesn’t come from adding more — it comes from letting things go.
Applying Kansō
In keeping with the meaning of kansō, there's really no need to overcomplicate the way you bring this concept into your life and practice.
Simplify your physical space by getting rid of objects that no longer serve you, stop buying things you don't need, avoid multitasking, and impose limits on the chatter you allow into your mind.
1. Simplify Your Environment
“The things you own end up owning you.” — Tyler Durden
The most obvious application of kansō is through the lens of minimalism — de-emphasizing your need for more things, more stimulation, and more status. Let go of the false idea that more = better.
Minimalism looks different for everyone. You don’t need to move into a tiny house and give away all your worldly possessions to embrace the spirit of kansō. For many, it simply means being more conscious about the things you buy and spending a little bit of effort from time to time to eliminate items that no longer serve you.
Capsule wardrobes, decluttered desks, and mindful purchasing habits are all modern echoes of this principle.
2. Simplify Your Mental Chatter
"Muddy water is best cleared by leaving it alone." — Alan Watts
Even more important is to simplify how we think and act. Multitasking, overthinking, and compulsive planning all add layers of mental clutter — the kind kansō encourages us to let go of. They create fragmentation — a thousand half-thoughts competing for attention instead of a single, clear thread of focus.
Perhaps the most impactful way we can apply kansō to our mental chatter is through a conscious limiting of the way we engage online.
To me, this means setting boundaries with how much noise I allow in from the digital world. The concept of a digital detox couldn’t be more relevant here. Every moment spent on social media, scrolling news feeds, or chasing vanity metrics clutters our minds and drains our attention from what matters.
Even something as simple as switching to a dumbphone or reserving one day a week free of computer screens can work to declutter our thoughts and simplify our daily rhythm. It's not about total disconnection, but simplifying the mental chatter we allow into our minds.
3. Simplify Your Desires
"Want less. Need less. Suffer less."
Another dimension of kansō is the release of mimetic desire — which is the unconscious force that causes us to want things simply because others do, rather than because they hold any real value for us.
Mimetic desire is a form of psychological maximalism — it creates a pile of new wants and desires from imagined needs that don't serve any real value, thereby diluting the meaning we gain from the things that do.
This example of kansō might be the most relevant to Zen as a whole, which emphasizes the importance of letting go of attachment — a practice that begins by releasing ourselves from the grip of desire.
Before buying something, stop and ask yourself, "Do I actually need this? Does it serve a real, practical purpose in my life that I'm not already getting from something else?"
I’ve found that giving myself a three-week waiting period before buying something helps me answer this question more honestly. If I still want it after three weeks, I can get it — but in about 90% of cases, I realize I didn’t actually need it after all and refrain from buying it.
4. Simplify Your Focus
"The hunter that chases two rabbits catches none."
Doing one thing well is always more powerful than doing five things halfway. To do this, we must commit ourselves fully to the task at hand, casting aside everything else — at least for a while.
This has become essential in my writing practice. I feel as though my best work almost always comes from sessions where I was able to ignore the rest of my never-ending to-do list, turned off my phone, and closed the 50 browser tabs I somehow always have open. It’s only when I remove the distractions completely that I can access the clarity — and the flow — needed to write something that actually makes sense.
Science backs this up, too — despite what many of us believe, we’re not actually capable of multitasking. What we’re really doing is rapidly switching between tasks, and every switch comes with a cognitive cost. It’s inefficient, mentally exhausting, and leads to poorer results across the board. Simplifying our focus is actually the best way to make the most use of your effort.
Kansō Aesthetics
It's impossible to discuss kansō without acknowledging its role as a design principle. In Japan, a country deeply rooted in Zen philosophy, the concept of kansō is recognized as one of the 7 core aesthetic pillars of wabi-sabi that inform both traditional and modern design.
These 7 principles include:
- Kansō (simplicity)
- Fukinsei (asymmetry)
- Shibui (subtle beauty)
- Shizen (naturalness)
- Yūgen (mystery)
- Datsuzoku (freedom from convention)
- Seijaku (stillness)
In design, kansō means much more than minimalism — it's a conscious effort to emphasize beauty and functionality through a process of elimination, rather than adornment or decoration.
By eliminating aspects that aren't totally necessary to form and function, designers are able to place more emphasis or draw more attention to the parts that matter most.
The result is a sort of quiet elegance. Nothing extra, nothing forced.
The most obvious applications of kansō are things like zen gardens, traditional Japanese tea rooms, or contemporary Japanese architecture.
Outside of Japan, you can find a masterful application of kansō in projects like Mies van der Rohe’s Farnsworth House, The Casa Wabi Foundation by Tadao Ando, or Peter Zumthor’s Therme Vals.
These are all high-profile examples of master architects, but kansō elements can be found all over the place. For example, this simple A-frame cabin — stripped-down, functional, and quietly beautiful. Or something as ordinary as a single-speed bike.
Kansō as a design principle can be applied to anything — clothing (Lemaire, COS), product design (Apple, Bang & Olufsen), furniture (Ikea, Muji), kitchenware (Hasami Porcelain, Heath Ceramics), and much more.
The application of kansō in design carries the same essential purpose as it does in life — to strip away what’s unnecessary so the parts that truly matter can stand out. In design, this means refining form and function. In life, this means reducing friction to create more space for a clear mind and genuine connection to the present moment.
 # A Simple Practice: Kansō
# A Simple Practice: KansōBefore you move on to the next thing, pause and take a look around you.
What’s one thing in your physical space, digital world, or daily routine that’s adding noise instead of meaning?
What would it feel like to let it go?
Subscribe to The Zen Psychedelic
Thanks for reading The Zen Psychedelic! Consider subscribing for free to receive new posts and support my work.
You can subscribe here using Nostr or follow me on Substack.
→ This post was originally published on The Zen Psychedelic Substack
-
 @ 1c19eb1a:e22fb0bc
2025-04-22 01:36:33
@ 1c19eb1a:e22fb0bc
2025-04-22 01:36:33After my first major review of Primal on Android, we're going to go a very different direction for this next review. Primal is your standard "Twitter clone" type of kind 1 note client, now branching into long-form. They also have a team of developers working on making it one of the best clients to fill that use-case. By contrast, this review will not be focusing on any client at all. Not even an "other stuff" client.
Instead, we will be reviewing a very useful tool created and maintained by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 called #Amber. For those unfamiliar with Amber, it is an #Android application dedicated to managing your signing keys, and allowing you to log into various #Nostr applications without having to paste in your private key, better known as your #nsec. It is not recommended to paste your nsec into various applications because they each represent another means by which it could be compromised, and anyone who has your nsec can post as you. On Nostr, your #npub is your identity, and your signature using your private key is considered absolute proof that any given note, reaction, follow update, or profile change was authorized by the rightful owner of that identity.
It happens less often these days, but early on, when the only way to try out a new client was by inputting your nsec, users had their nsec compromised from time to time, or they would suspect that their key may have been compromised. When this occurs, there is no way to recover your account, or set a new private key, deprecating the previous one. The only thing you can do is start over from scratch, letting everyone know that your key has been compromised and to follow you on your new npub.
If you use Amber to log into other Nostr apps, you significantly reduce the likelihood that your private key will be compromised, because only one application has access to it, and all other applications reach out to Amber to sign any events. This isn't quite as secure as storing your private key on a separate device that isn't connected to the internet whatsoever, like many of us have grown accustomed to with securing our #Bitcoin, but then again, an online persona isn't nearly as important to secure for most of us as our entire life savings.
Amber is the first application of its kind for managing your Nostr keys on a mobile device. nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 didn't merely develop the application, but literally created the specification for accomplishing external signing on Android which can be found in NIP-55. Unfortunately, Amber is only available for Android. A signer application for iOS is in the works from nostr:npub1yaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgs3tvjmf, but is not ready for use at this time. There is also a new mobile signer app for Android and iOS called Nowser, but I have not yet had a chance to try this app out. From a cursory look at the Android version, it is indeed in the very early stages of development and cannot be compared with Amber.
This review of Amber is current as of version 3.2.5.
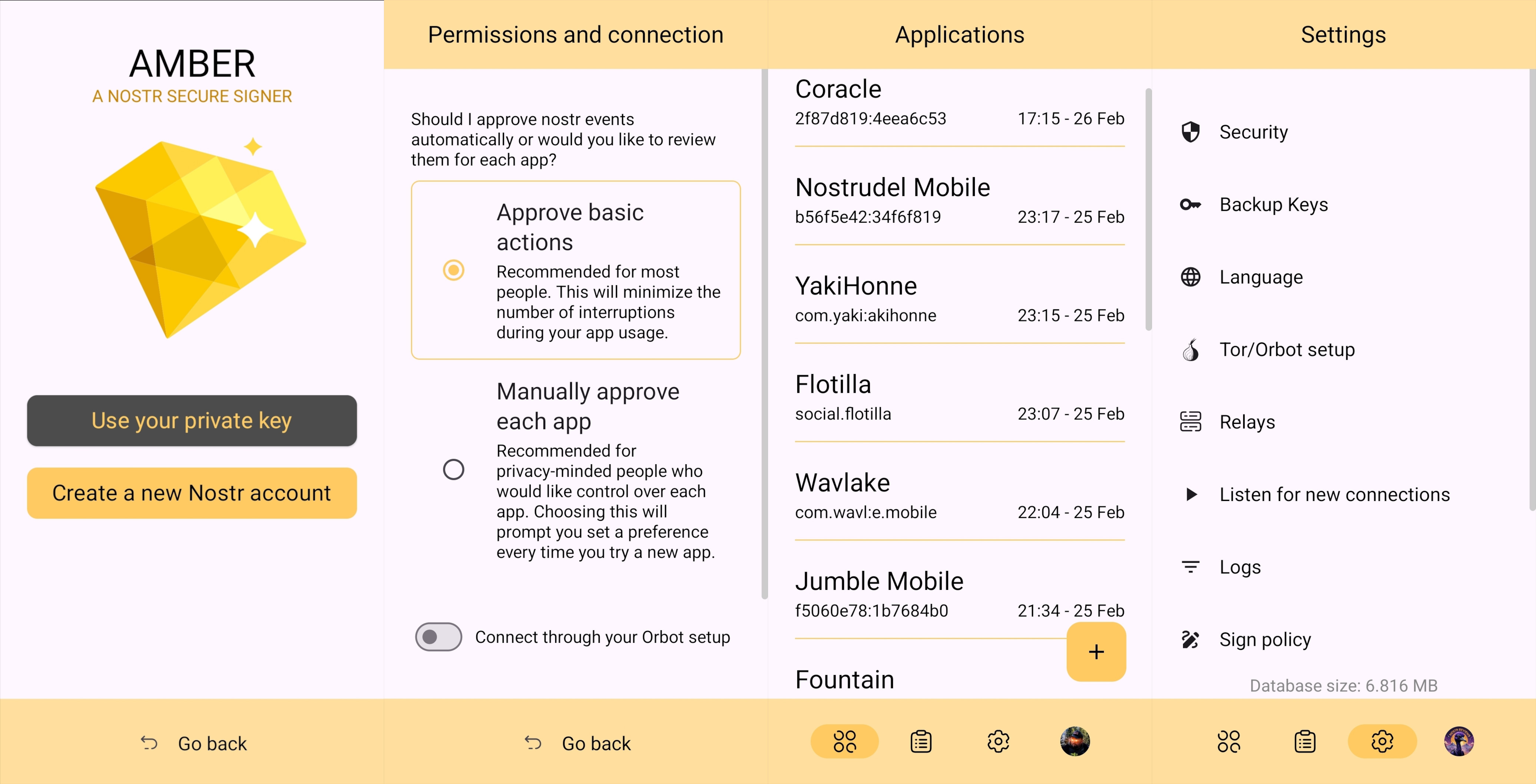
Overall Impression
Score: 4.7 / 5 (Updated 4/21/2025)
I cannot speak highly enough about Amber as a tool that every Nostr user on Android should start using if they are not already. When the day comes that we have more options for well-developed signer apps on mobile, my opinion may very well change, but until then Amber is what we have available to us. Even so, it is an incredibly well thought-out and reliable tool for securing your nsec.
Despite being the only well-established Android signer available for Android, Amber can be compared with other external signing methods available on other platforms. Even with more competition in this arena, though, Amber still holds up incredibly well. If you are signing into web applications on a desktop, I still would recommend using a browser extension like #Alby or #Nos2x, as the experience is usually faster, more seamless, and far more web apps support this signing method (NIP-07) than currently support the two methods employed by Amber. Nevertheless that gap is definitely narrowing.
A running list I created of applications that support login and signing with Amber can be found here: Nostr Clients with External Signer Support
I have run into relatively few bugs in my extensive use of Amber for all of my mobile signing needs. Occasionally the application crashes when trying to send it a signing request from a couple of applications, but I would not be surprised if this is no fault of Amber at all, and rather the fault of those specific apps, since it works flawlessly with the vast majority of apps that support either NIP-55 or NIP-46 login.
I also believe that mobile is the ideal platform to use for this type of application. First, because most people use Nostr clients on their phone more than on a desktop. There are, of course, exceptions to that, but in general we spend more time on our phones when interacting online. New users are also more likely to be introduced to Nostr by a friend having them download a Nostr client on their phone than on a PC, and that can be a prime opportunity to introduce the new user to protecting their private key. Finally, I agree with the following assessment from nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn.
nostr:nevent1qqsw0r6gzn05xg67h5q2xkplwsuzedjxw9lf7ntrxjl8ajm350fcyugprfmhxue69uhhyetvv9ujumn0wd68yurvv438xtnrdaksyg9hyaxj3clfswlhyrd5kjsj5v04clhjvgeq6pwztmysfzdvn93gev7awu9v
The one downside to Amber is that it will be quite foreign for new users. That is partially unavoidable with Nostr, since folks are not accustomed to public/private key cryptography in general, let alone using a private key to log into websites or social media apps. However, the initial signup process is a bit cumbersome if Amber is being used as the means of initially generating a key pair. I think some of this could be foregone at start-up in favor of streamlining onboarding, and then encourage the user to back-up their private key at a later time.
Features
Amber has some features that may surprise you, outside of just storing your private key and signing requests from your favorite Nostr clients. It is a full key management application, supporting multiple accounts, various backup methods, and even the ability to authorize other users to access a Nostr profile you control.
Android Signing
This is the signing method where Amber really shines in both speed and ease of use. Any Android application that supports this standard, and even some progressive web-apps that can be installed to your Android's home-screen, can very quickly and seamlessly connect with Amber to authorize anything that you need signed with your nsec. All you have to do is select "Login with Amber" in clients like #Amethyst or #0xChat and the app will reach out to Amber for all signing requests from there on out. If you had previously signed into the app with your nsec, you will first need to log out, then choose the option to use Amber when you log back in.
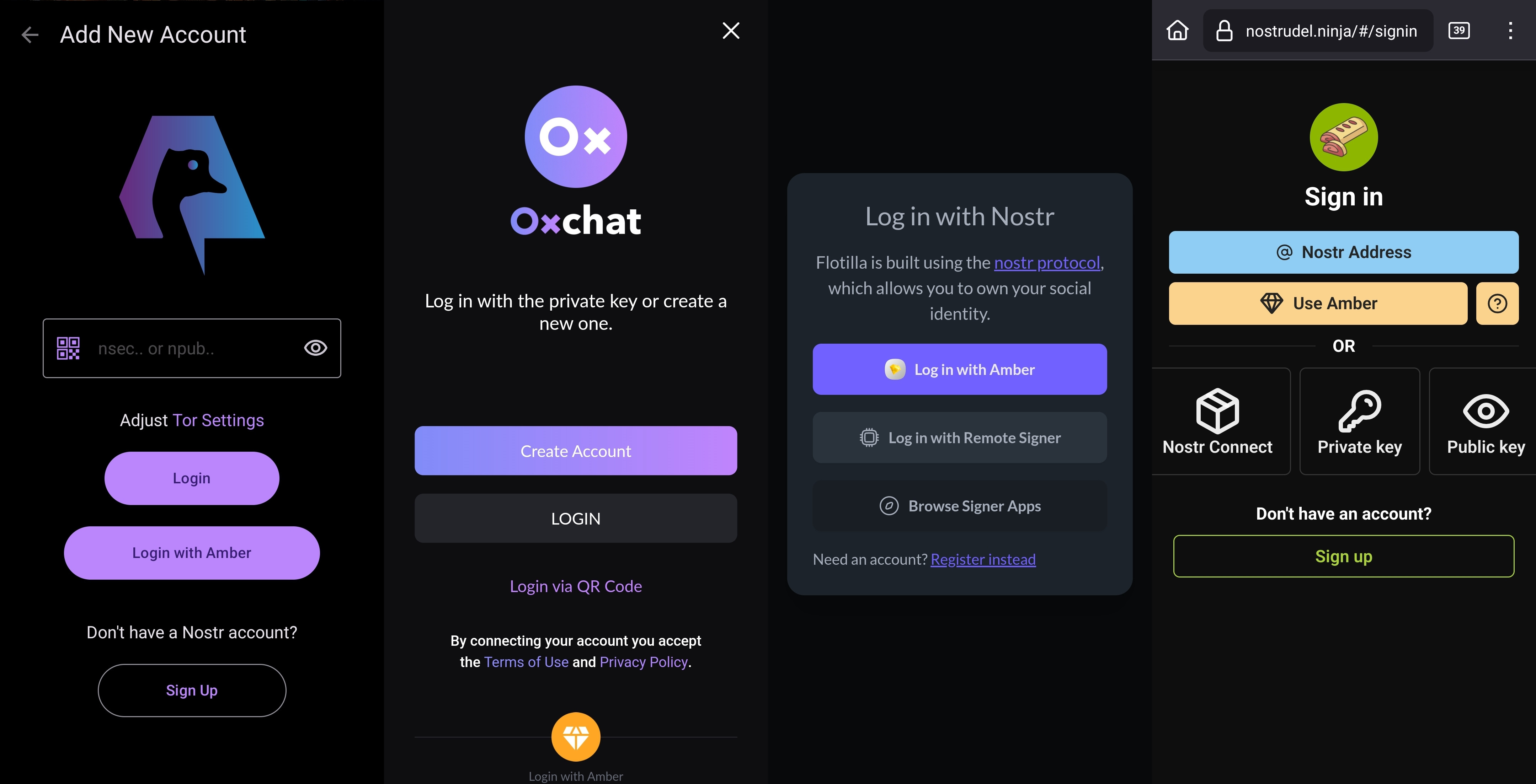
This is a massive deal, because everything you do on Nostr requires a signature from your private key. Log in? Needs a signature. Post a "GM" note? Needs a signature. Follow someone who zapped your note? Needs a signature. Zap them back? You guessed it; needs a signature. When you paste your private key into an application, it will automatically sign a lot of these actions without you ever being asked for approval, but you will quickly realize just how many things the client is doing on your behalf when Amber is asking you to approve them each time.
Now, this can also get quite annoying after a while. I recommend using the setting that allows Amber to automatically sign for basic functions, which will cut down on some of the authorization spam. Once you have been asked to authorize the same type of action a few times, you can also toggle the option to automatically authorize that action in the future. Don't worry, though, you have full control to require Amber to ask you for permission again if you want to be alerted each time, and this toggle is specific to each application, so it's not a blanket approval for all Nostr clients you connect with.
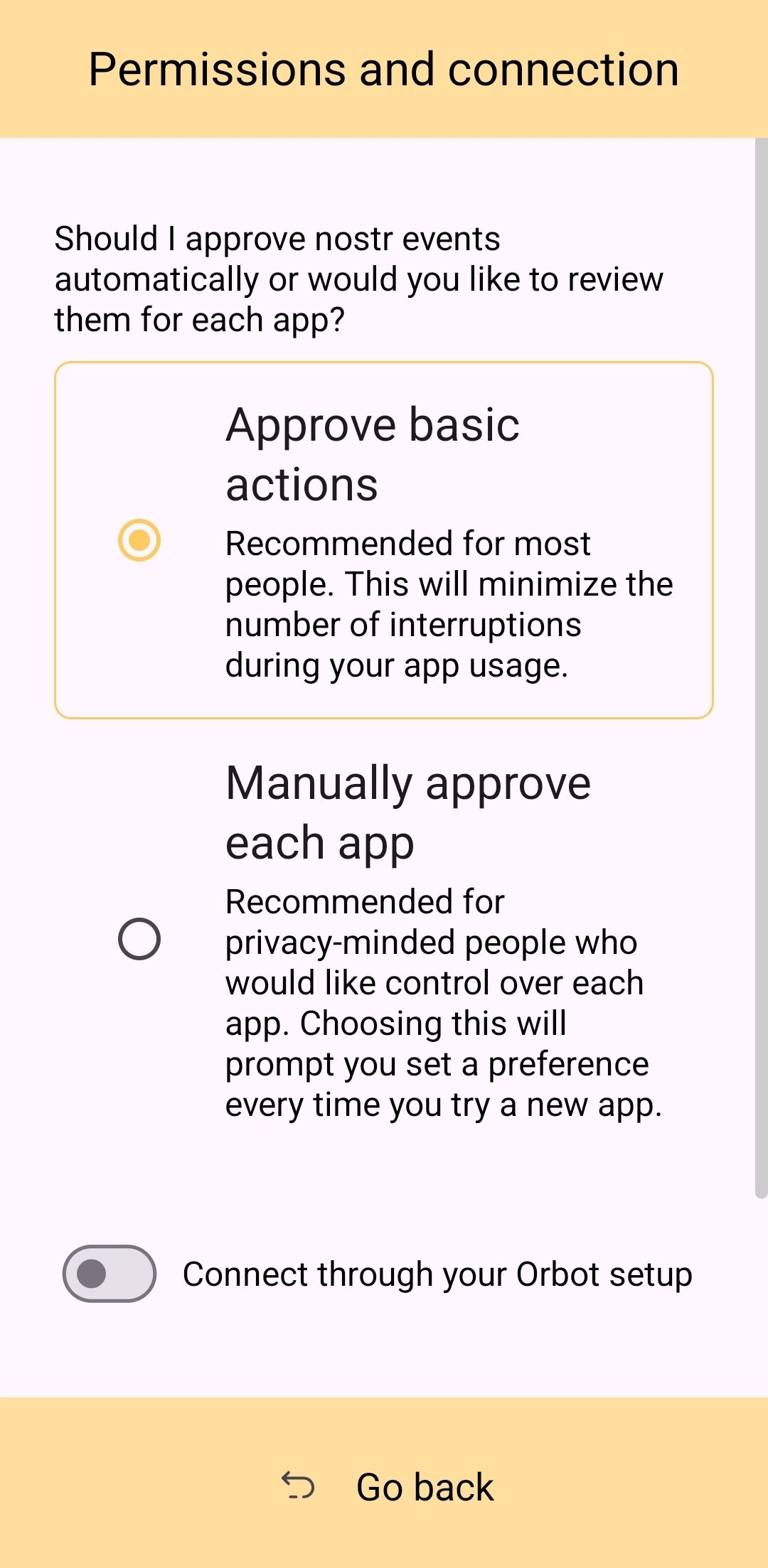
This method of signing is just as fast as signing via browser extension on web clients, which users may be more accustomed to. Everything is happening locally on the device, so it can be very snappy and secure.
Nostr Connect/Bunker Signing
This next method of signing has a bit of a delay, because it is using a Nostr relay to send encrypted information back and forth between the app the user is interacting with and Amber to obtain signatures remotely. It isn't a significant delay most of the time, but it is just enough to be noticeable.
Also, unlike the previous signing method that would automatically switch to Amber as the active application when a signing request is sent, this method only sends you a notification that you must be watching for. This can lead to situations where you are wondering why something isn't working in a client you signed into remotely, because it is waiting on you to authorize the action and you didn't notice the notification from Amber. As you use the application, you get used to the need to check for such authorization requests from time to time, or when something isn't working as expected.
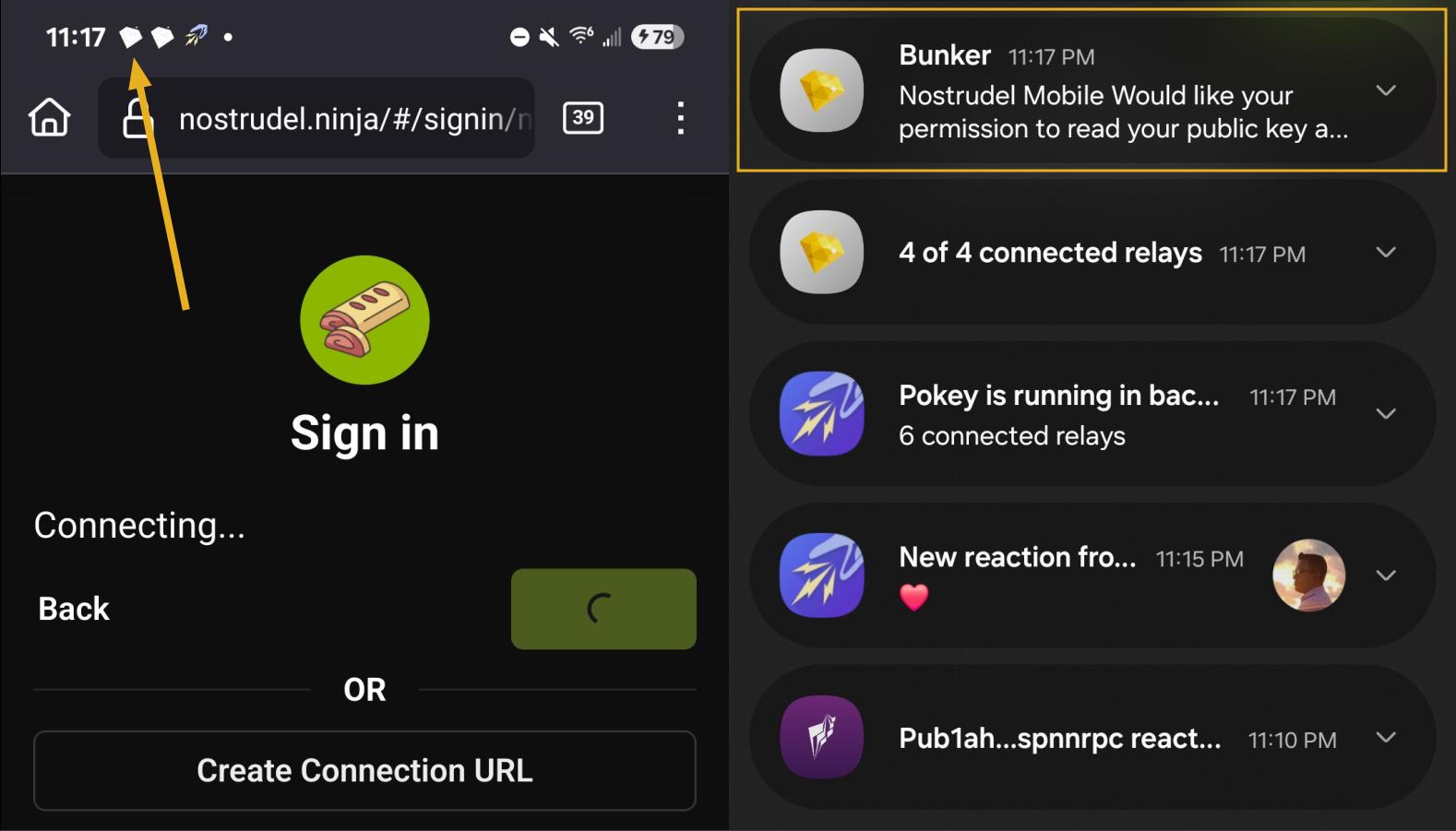
By default, Amber will use relay.nsec.app to communicate with whichever Nostr app you are connecting to. You can set a different relay for this purpose, if you like, though not just any relay will support the event kinds that Amber uses for remote signing. You can even run your own relay just for your own signing purposes. In fact, the creator of Amber has a relay application you can run on your phone, called Citrine, that can be used for signing with any web app you are using locally on your phone. This is definitely more of an advanced option, but it is there for you if you want it. For most users, sticking with relay.nsec.app will be just fine, especially since the contents of the events sent back and forth for signing are all encrypted.
Something many users may not realize is that this remote signing feature allows for issuing signing permissions to team members. For instance, if anyone ever joined me in writing reviews, I could issue them a connection string from Amber, and limit their permissions to just posting long-form draft events. Anything else they tried to do would require my explicit approval each time. Moreover, I could revoke those permissions if I ever felt they were being abused, without the need to start over with a whole new npub. Of course, this requires that your phone is online whenever a team member is trying to sign using the connection string you issued, and it requires you pay attention to your notifications so you can approve or reject requests you have not set to auto-approve. However, this is probably only useful for small teams, and larger businesses will want to find a more robust solution for managing access to their npub, such as Keycast from nostr:npub1zuuajd7u3sx8xu92yav9jwxpr839cs0kc3q6t56vd5u9q033xmhsk6c2uc.
The method for establishing a connection between Amber and a Nostr app for remote signing can vary for each app. Most, at minimum, will support obtaining a connection string from Amber that starts with "bunker://" and pasting it in at the time of login. Then you just need to approve the connection request from Amber and the client will log you in and send any subsequent signing requests to Amber using the same connection string.
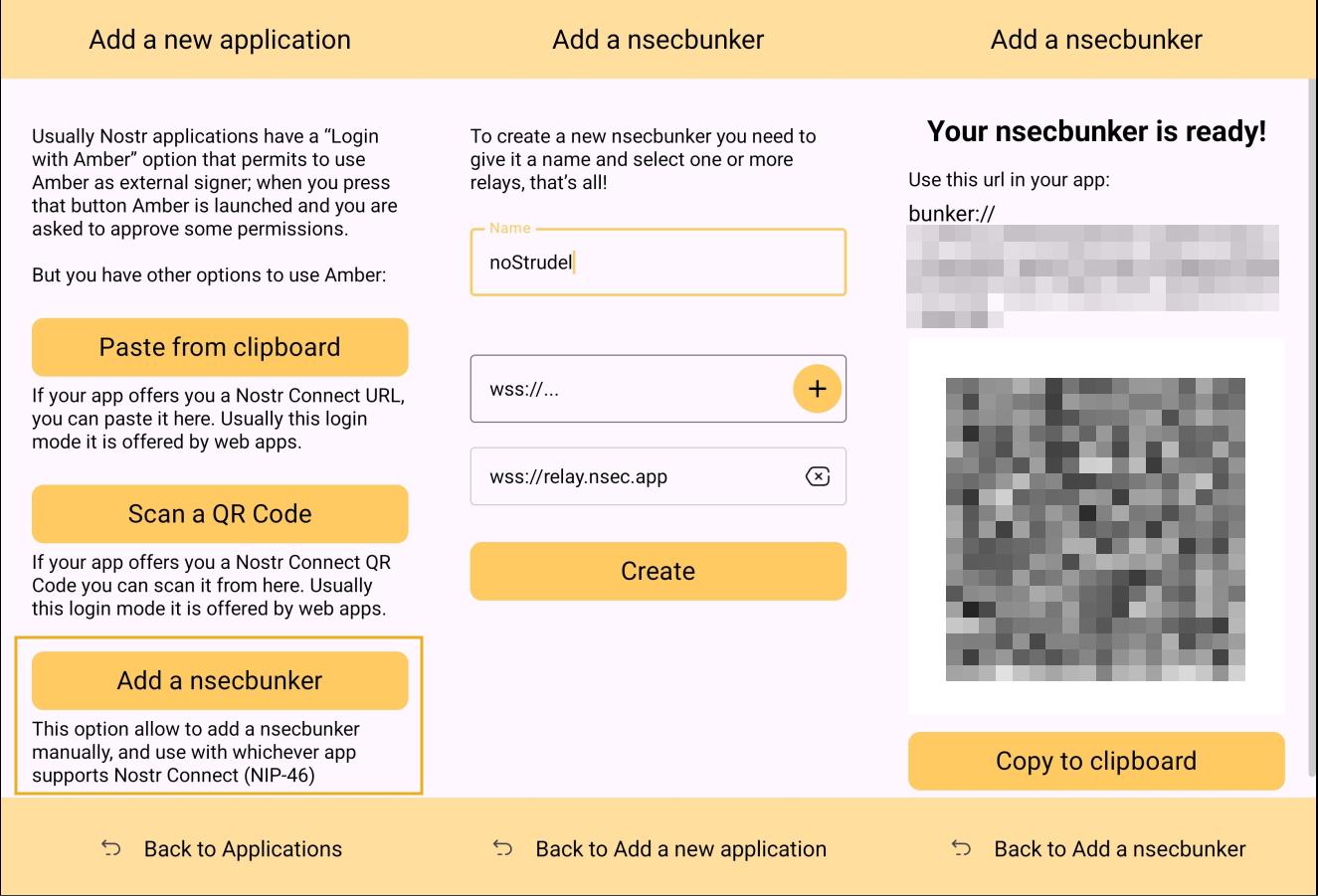
Some clients will also offer the option to scan a QR code to connect the client to Amber. This is quite convenient, but just remember that this also means the client is setting which relay will be used for communication between the two. Clients with this option will also have a connection string you can copy and paste into Amber to achieve the same purpose. For instance, you may need this option if you are trying to connect to an app on your phone and therefore can't scan the QR code using Amber on the same phone.
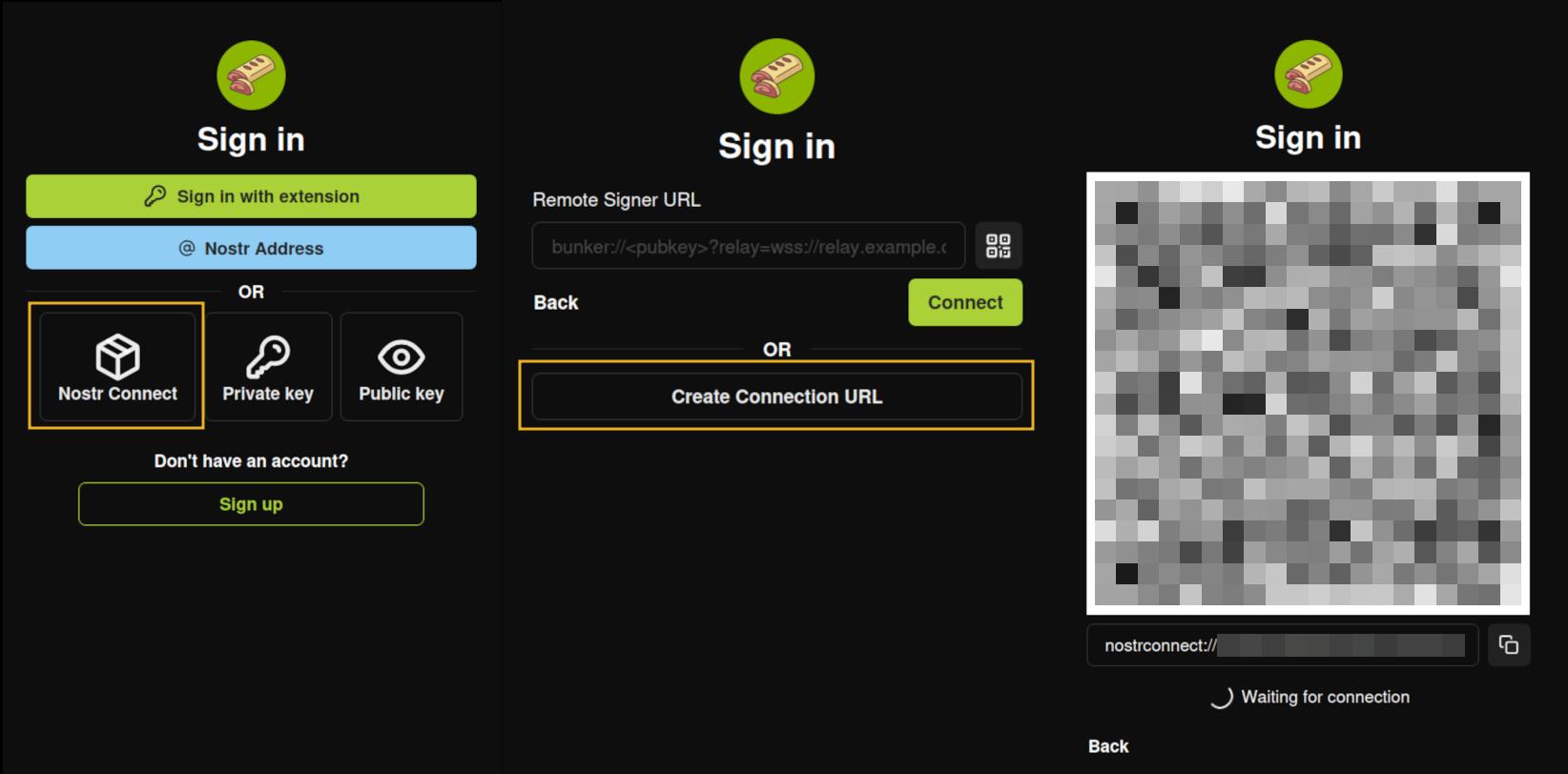
Multiple Accounts
Amber does not lock you into using it with only a single set of keys. You can add all of your Nostr "accounts" to Amber and use it for signing events for each independently. Of course, Nostr doesn't actually have "accounts" in the traditional sense. Your identity is simply your key-pair, and Amber stores and accesses each private key as needed.
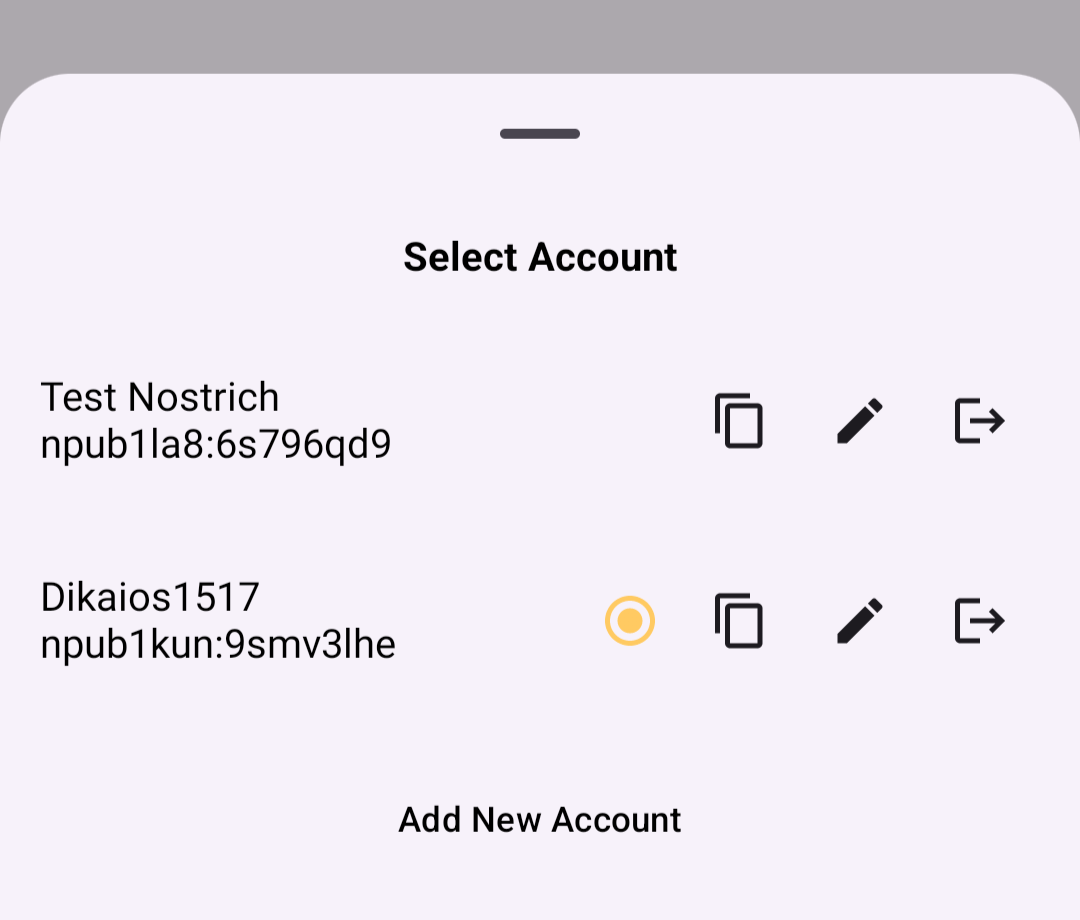
When first signing in using native Android signing as described above, Amber will default to whichever account was most recently selected, but you can switch to the account that is needed before approving the request. After initial login, Amber will automatically detect the account that the signing request is for.
Key Backup & Restore
Amber allows multiple ways to back up your private key. As most users would expect, you can get your standard nsec and copy/paste it to a password manager, but you can also obtain your private key as a list of mnemonic seed words, an encrypted version of your key called an ncryptsec, or even a QR code of your nsec or ncryptsec.
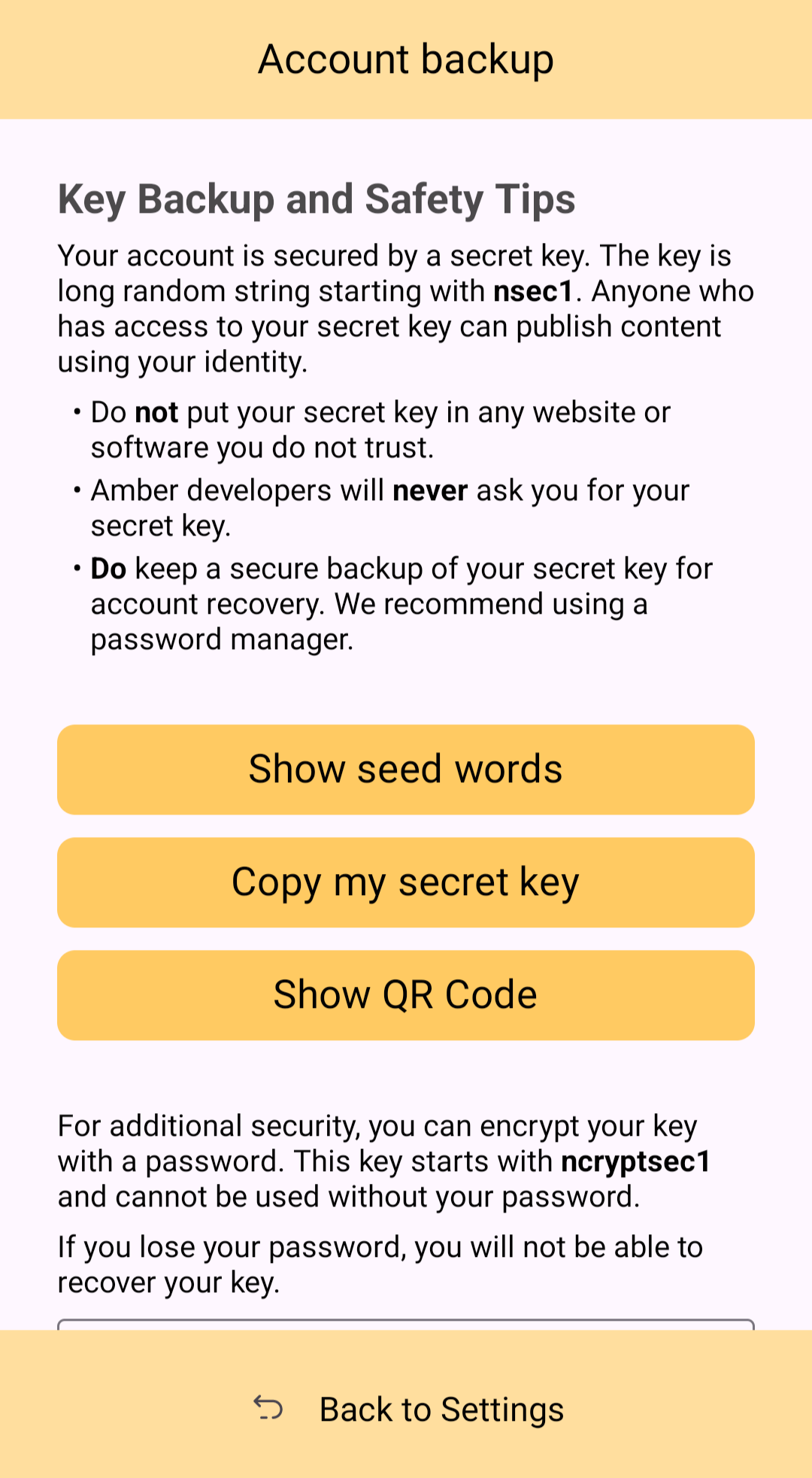
Additionally, in order to gain access to this information, Amber requires you to enter your device's PIN or use biometric authentication. This isn't cold-storage level protection for your private key by any means, especially since your phone is an internet connected device and does not store your key within a secure element, but it is about as secure as you can ask for while having your key accessible for signing Nostr events.
Tor Support
While Amber does not have Tor support within the app itself, it does support connecting to Tor through Orbot. This would be used with remote signing so that Amber would not connect directly over clearnet to the relay used for communication with the Nostr app requesting the signature. Instead, Amber would connect through Tor, so the relay would not see your IP address. This means you can utilize the remote signing option without compromising your anonymity.
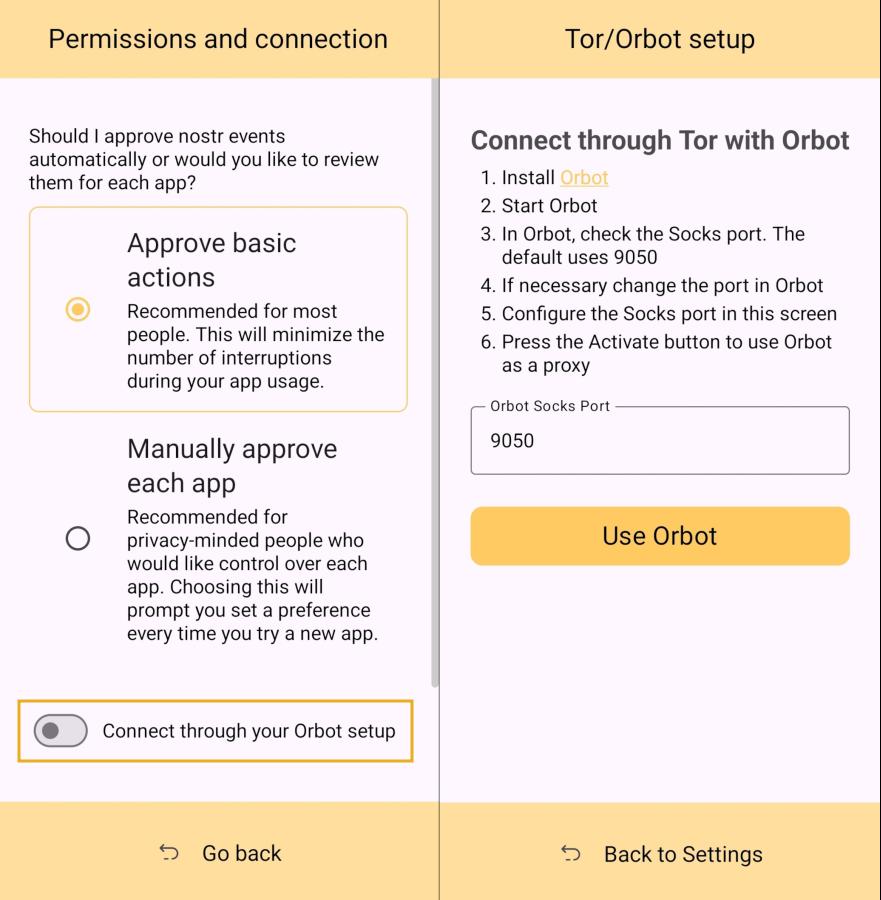
Additional Security
Amber allows the user the option to require either biometric or PIN authentication before approving signing requests. This can provide that extra bit of assurance that no one will be able to sign events using your private key if they happen to gain access to your phone. The PIN you set in Amber is also independent from the PIN to unlock your device, allowing for separation of access.
Can My Grandma Use It?
Score: 4.6 / 5 (Updated 4/21/2025)
At the end of the day, Amber is a tool for those who have some concept of the importance of protecting their private key by not pasting it into every Nostr client that comes along. This concept in itself is not terribly approachable to an average person. They are used to just plugging their password into every service they use, and even worse, they usually have the same password for everything so they can more readily remember it. The idea that they should never enter their "Nostr password" into any Nostr application would never occur to them unless someone first explained how cryptography works related to public/private key pairs.
That said, I think there can be some improvements made to how users are introduced to these concepts, and that a signer application like Amber might be ideal for the job. Considering Amber as a new user's first touch-point with Nostr, I think it holds up well, but could be somewhat streamlined.
Upon opening the app, the user is prompted to either use their existing private key or "Create a new Nostr account." This is straightforward enough. "Account" is not a technically correct term with Nostr, but it is a term that new users would be familiar with and understand the basic concept.
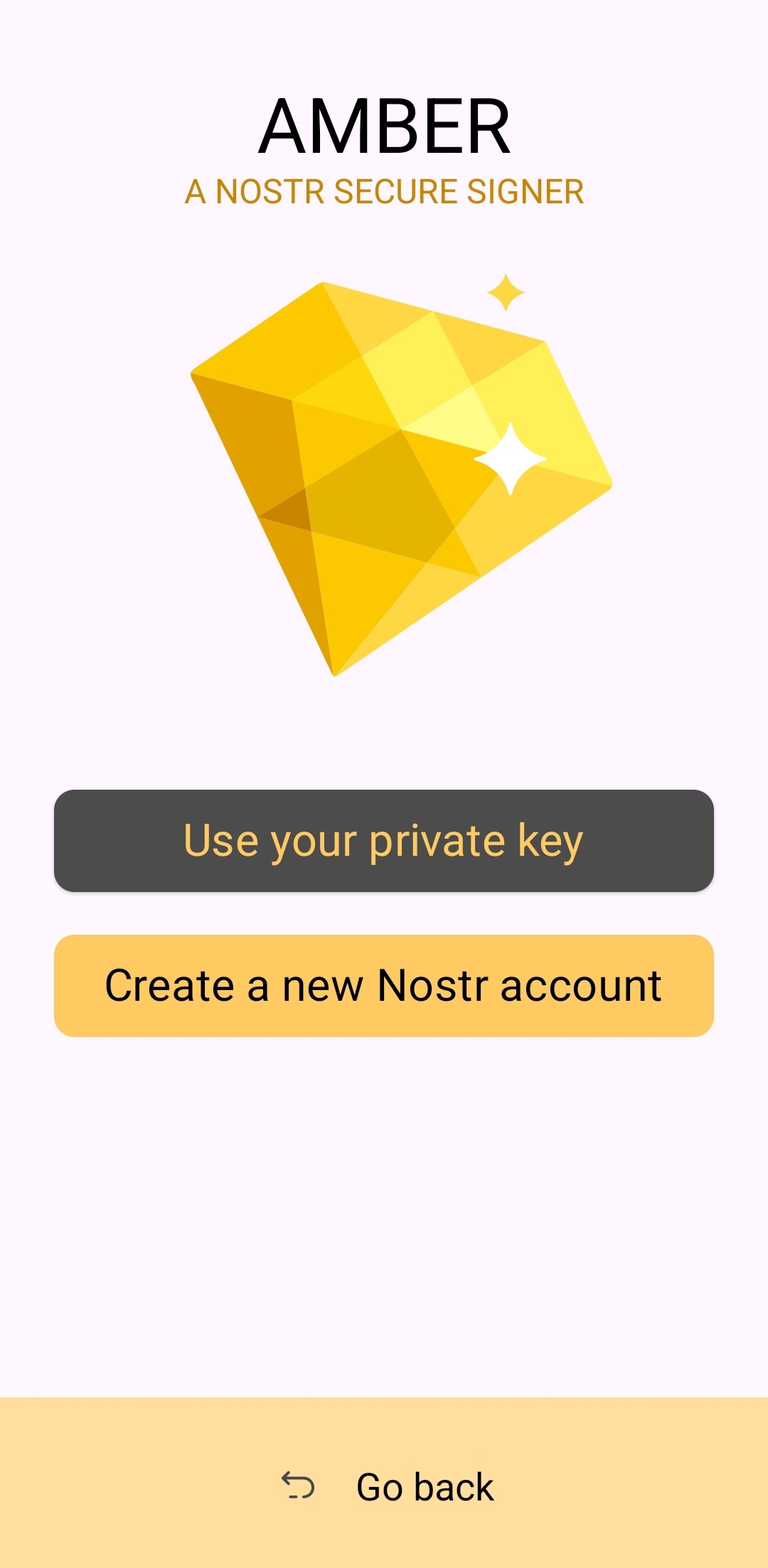
The next screen announces that the account is ready, and presents the user with their public key, explaining that it is "a sort of username" that will allow others to find them on Nostr. While it is good to explain this to the user, it is unnecessary information at this point. This screen also prompts the user to set a nickname and set a password to encrypt their private key. Since the backup options also allow the user to set this password, I think this step could be pushed to a later time. This screen would better serve the new user if it simply prompted them to set a nickname and short bio that could be saved to a few default relays.
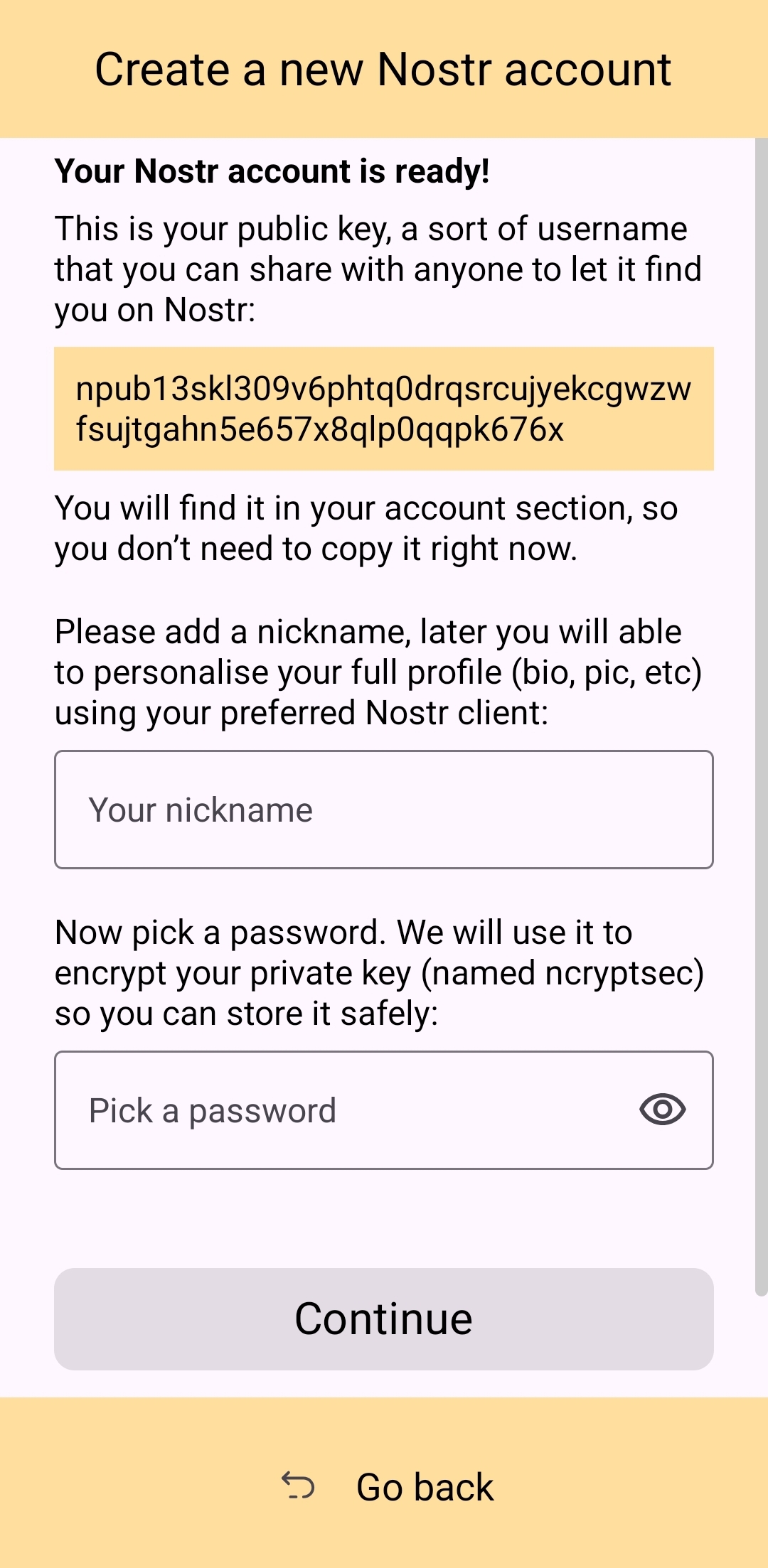
Of course, Amber is currently prompting for a password to be set up-front because the next screen requires the new user to download a "backup kit" in order to continue. While I do believe it is a good idea to encourage the creation of a backup, it is not crucial to do so immediately upon creation of a new npub that has nothing at stake if the private key is lost. This is something the UI could remind the user to do at a later time, reducing the friction of profile creation, and expediting getting them into the action.
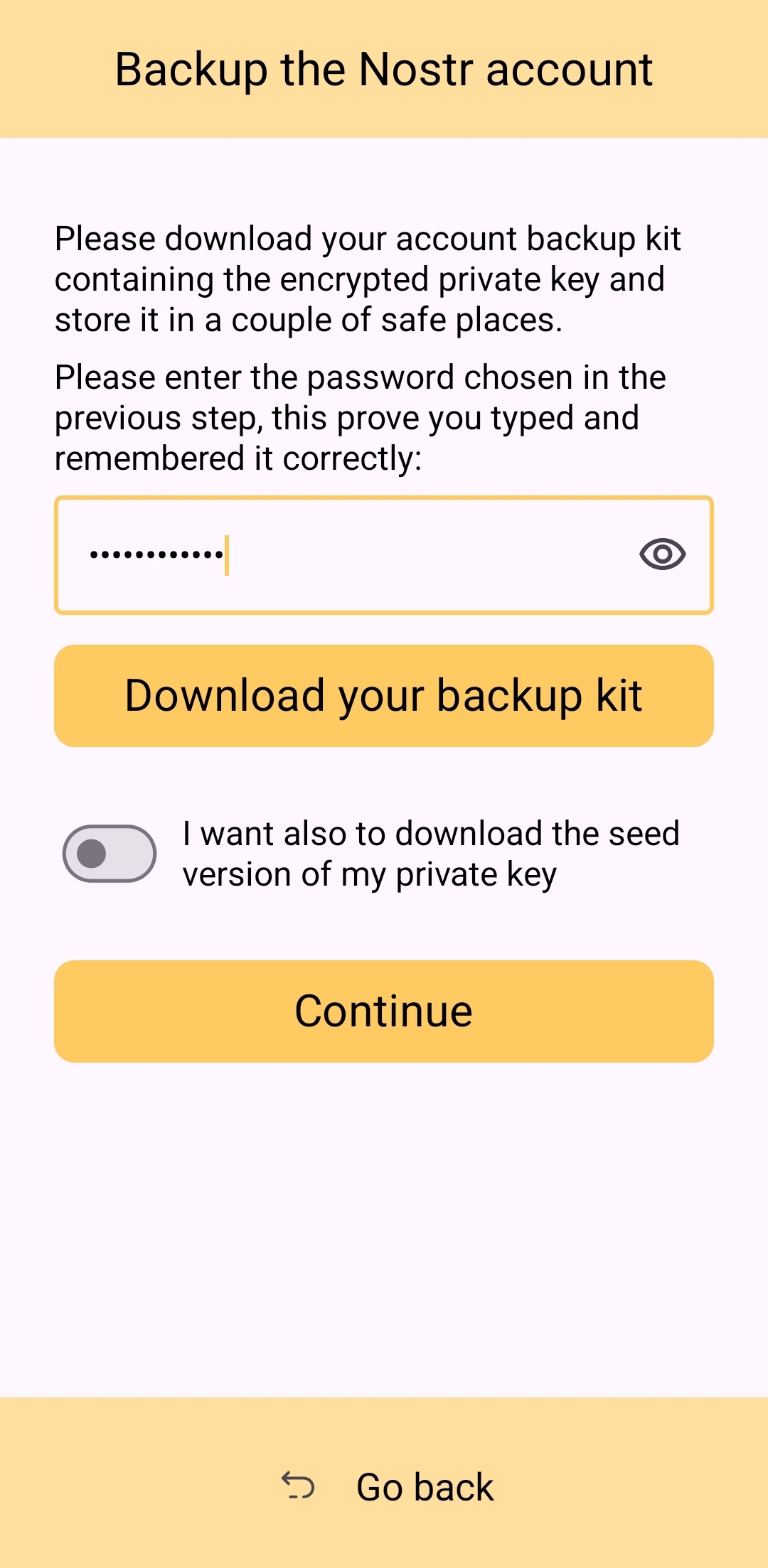
Outside of these minor onboarding friction points, I think Amber does a great job of explaining to the user the purpose of each of its features, all within the app and without any need to reference external documentation. As long as the user understands the basic concept that their private key is being stored by Amber in order to sign requests from other Nostr apps, so they don't have to be given the private key, Amber is very good about explaining the rest without getting too far into the technical weeds.
The most glaring usability issue with Amber is that it isn't available in the Play Store. Average users expect to be able to find applications they can trust in their mobile device's default app store. There is a valid argument to be made that they are incorrect in this assumption, but that doesn't change the fact that this is the assumption most people make. They believe that applications in the Play Store are "safe" and that anything they can't install through the Play Store is suspect. The prompts that the Android operating system requires the user to approve when installing "unknown apps" certainly doesn't help with this impression.
Now, I absolutely love the Zapstore from nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9, but it doesn't do much to alleviate this issue. Users will still need to be convinced that it is safe to install the Zapstore from the GitHub repo, and then install Amber from there. Furthermore, this adds yet another step to the onboarding process.
Instead of:
- Install Amber
- Set up your keys
- Install the client you want to use
- Log in with Amber
The process becomes:
- Go to the Zapstore GitHub and download the latest version from the releases page.
- Install the APK you downloaded, allowing any prompt to install unknown apps.
- Open Zapstore and install Amber, allowing any prompt to install unknown apps again.
- Open Amber and set up your keys.
- Install the client you want to use
- Log in with Amber
An application as important as Amber for protecting users' private keys should be as readily available to the new user as possible. New users are the ones most prone to making mistakes that could compromise their private keys. Amber should be available to them in the Play Store.
UPDATE: As of version 3.2.8 released on 4/21/2025, the onboarding flow for Amber has been greatly improved! Now, when selecting to set up a new "account" the user is informed on the very next screen, "Your Nostr account is ready!" and given their public key/npub. The only field the user must fill in is their "nickname"/display name and hit "Continue."
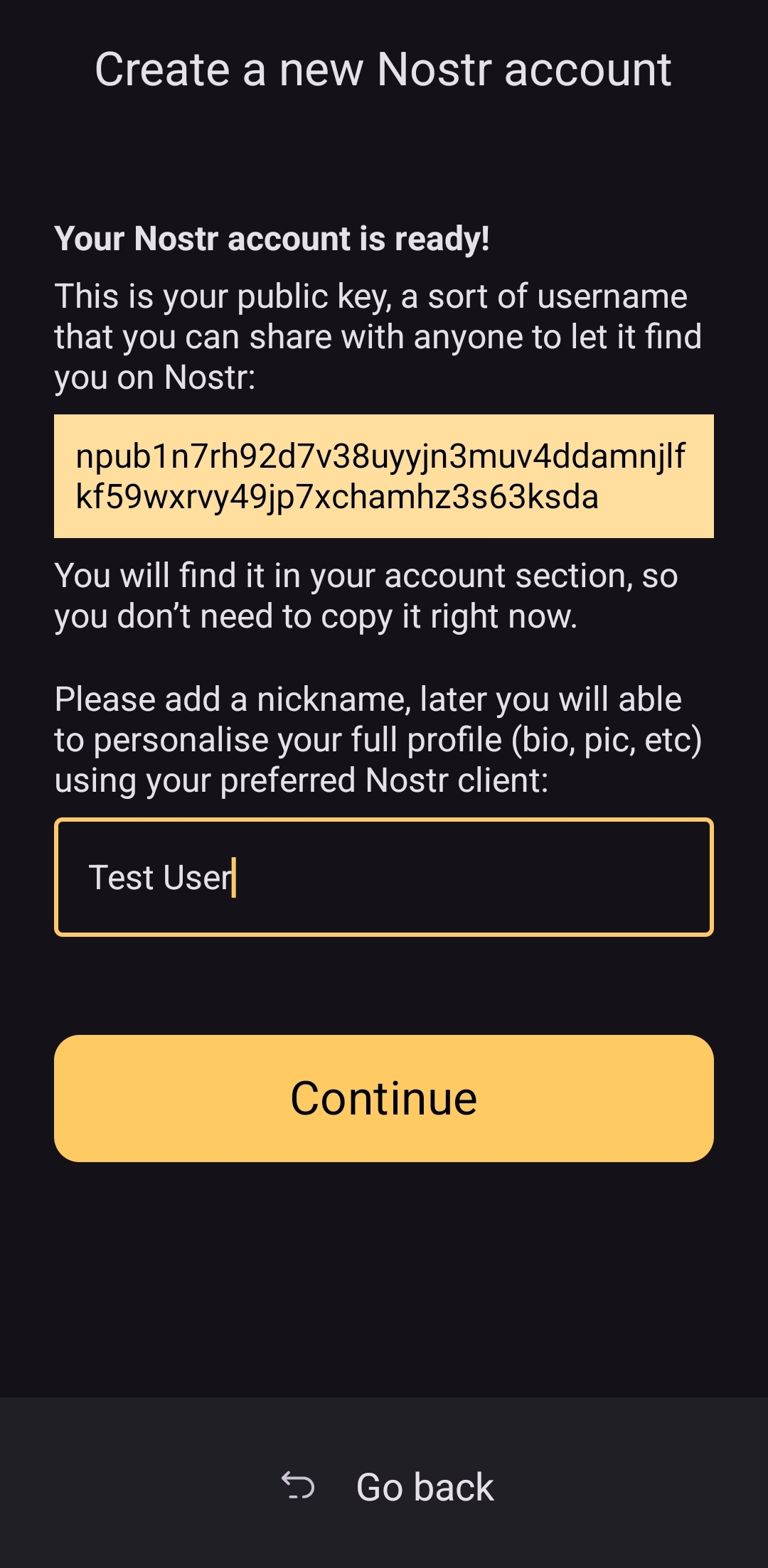
From there the user is asked if they want Amber to automatically approve basic actions, or manually approve each app, and then they are shown a new Applications screen, with a prompt to create a backup of their account. This prompt persists until the user has done so.
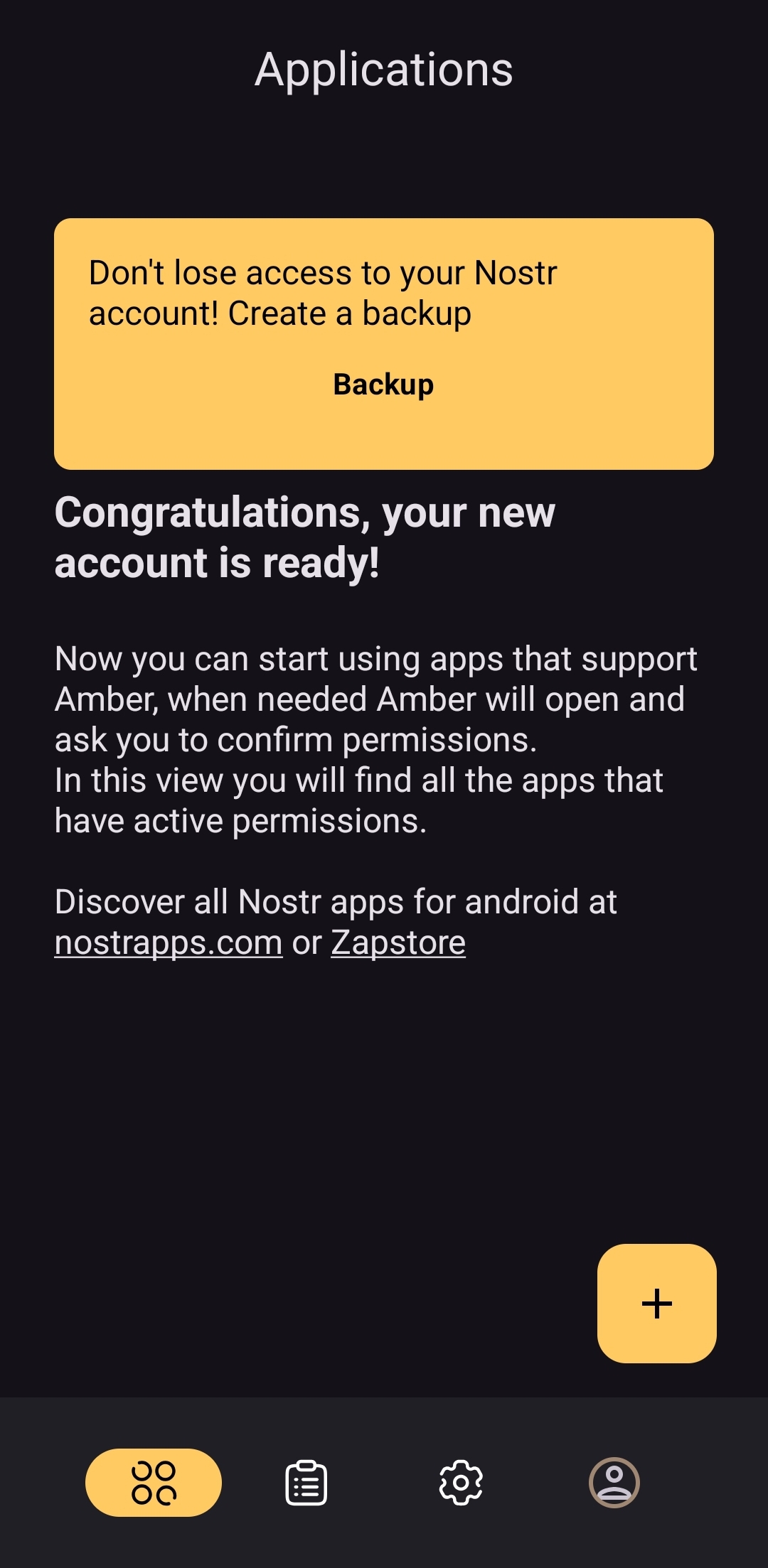
As you can see, the user is also encouraged to find applications that can be used with Amber with links to nostrapps.com and the Zapstore.
Thanks to these updates, Amber is now the smoothest and most user-friendly onboarding experience I have seen for Nostr to date. Sure, it doesn't have anything for setting up a profile picture or lightning address, but that is better done in a client like Amethyst or YakiHonne, anyway. Just tap "create," type in a handle to call yourself, and you're done!
How do UI Look?
Score: 4.5 / 5
Amber's UI can be described as clean but utilitarian. But then, Amber is a tool, so this is somewhat expected. It is not an app you will be spending a lot of time in, so the UI just needs to be serviceable. I would say it accomplishes this and then some. UI elements are generally easy to understand what they do, and page headings fill in the gaps where that is not the case.
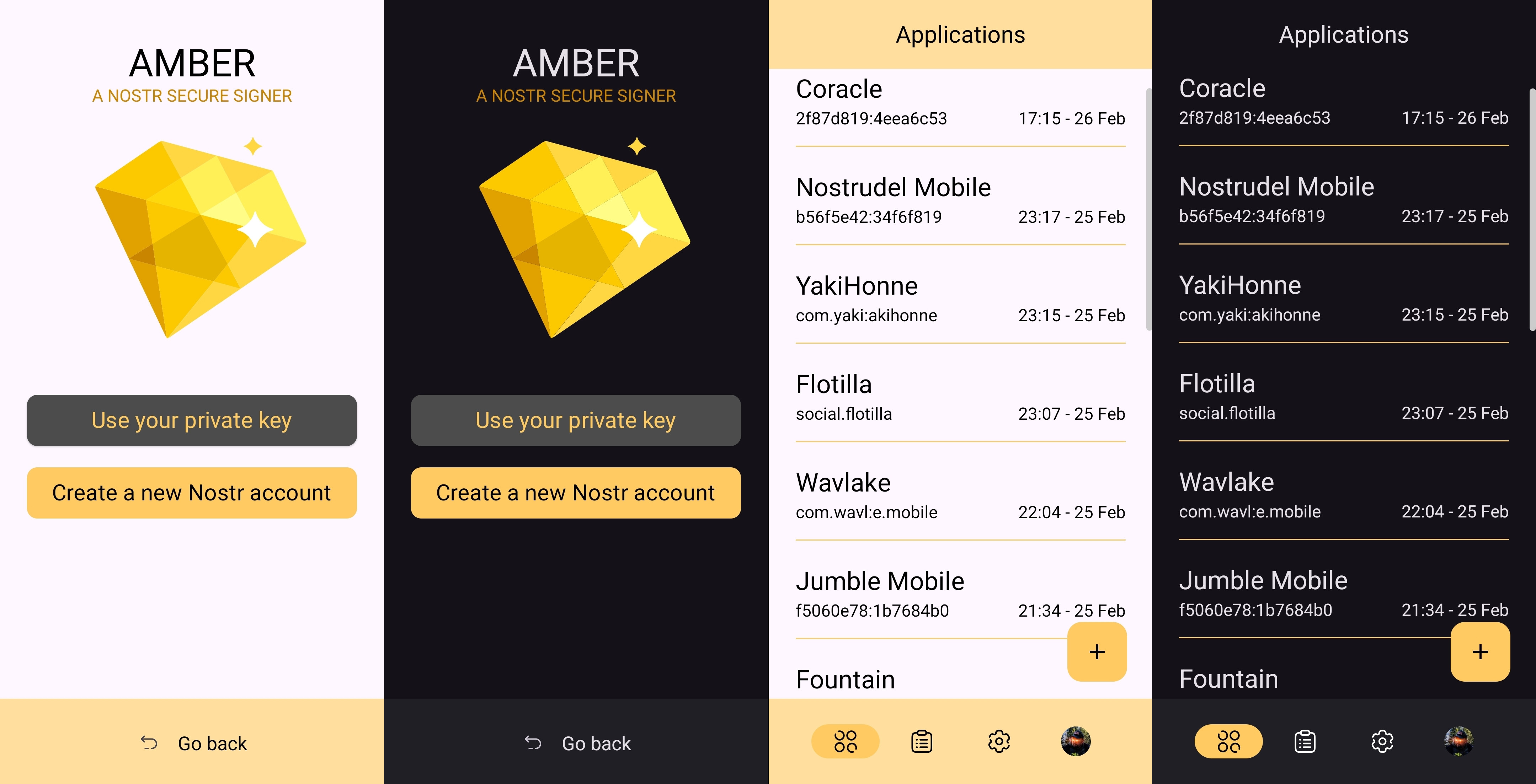
I am not the biggest fan of the color-scheme, particularly in light-mode, but it is not bad in dark-mode at all, and Amber follows whatever theme you have set for your device in that respect. Additionally, the color choice does make sense given the application's name.
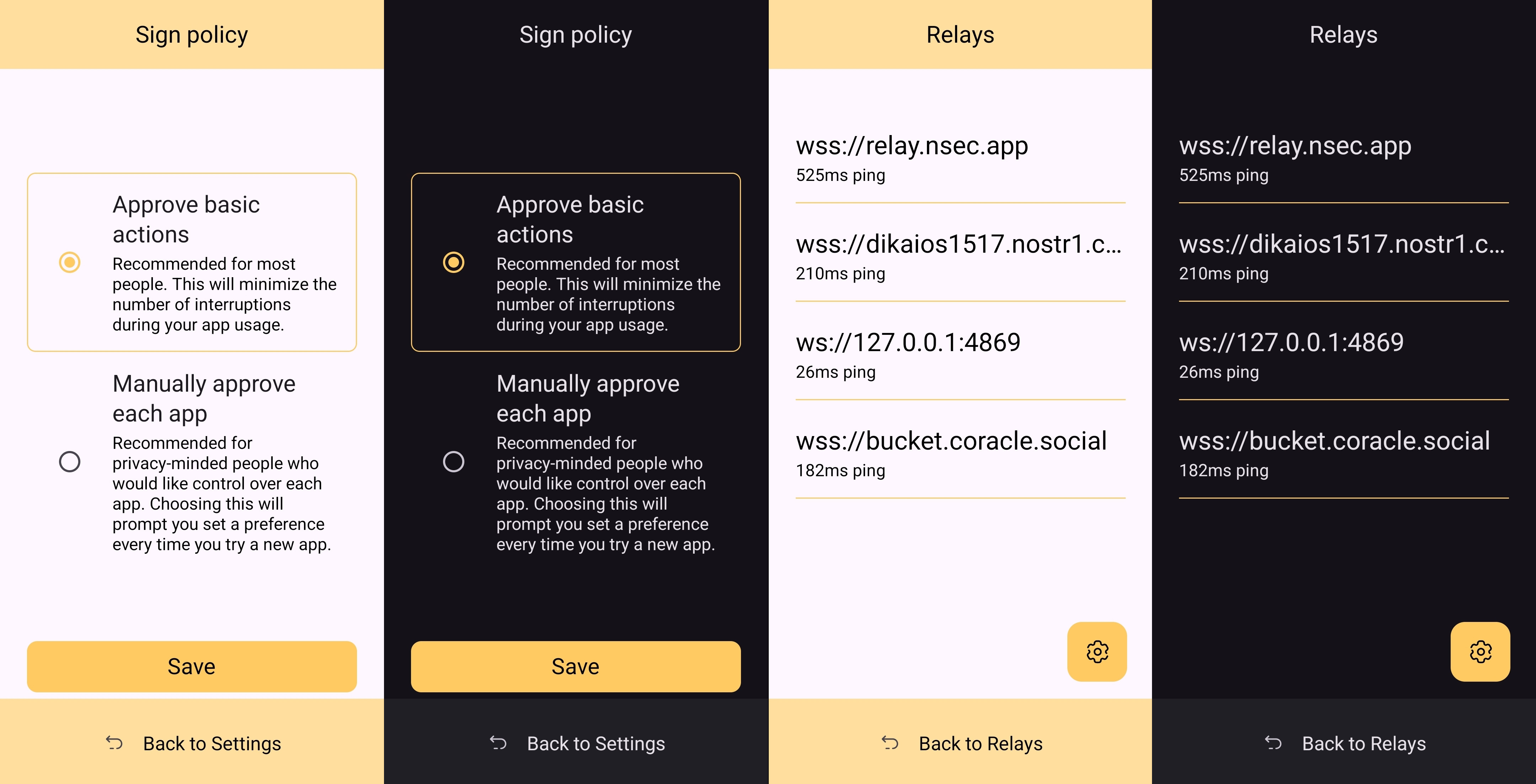
It must also be taken into consideration that Amber is almost entirely the product of a single developer's work. He has done a great job producing an app that is not only useful, but pleasant to interact with. The same cannot be said for most utility apps I have previously used, with interfaces that clearly made good design the lowest priority. While Amber's UI may not be the most beautiful Nostr app I have seen, design was clearly not an afterthought, either, and it is appreciated.
Relay Management
Score: 4.9 / 5
Even though Amber is not a Nostr client, where users can browse notes from their favorite npubs, it still relies heavily on relays for some of its features. Primarily, it uses relays for communicating with other Nostr apps for remote signing requests. However, it also uses relays to fetch profile data, so that each private key you add to Amber will automatically load your chosen username and profile picture.
In the relay settings, users can choose which relays are being used to fetch profile data, and which relays will be used by default when creating new remote signing connection strings.
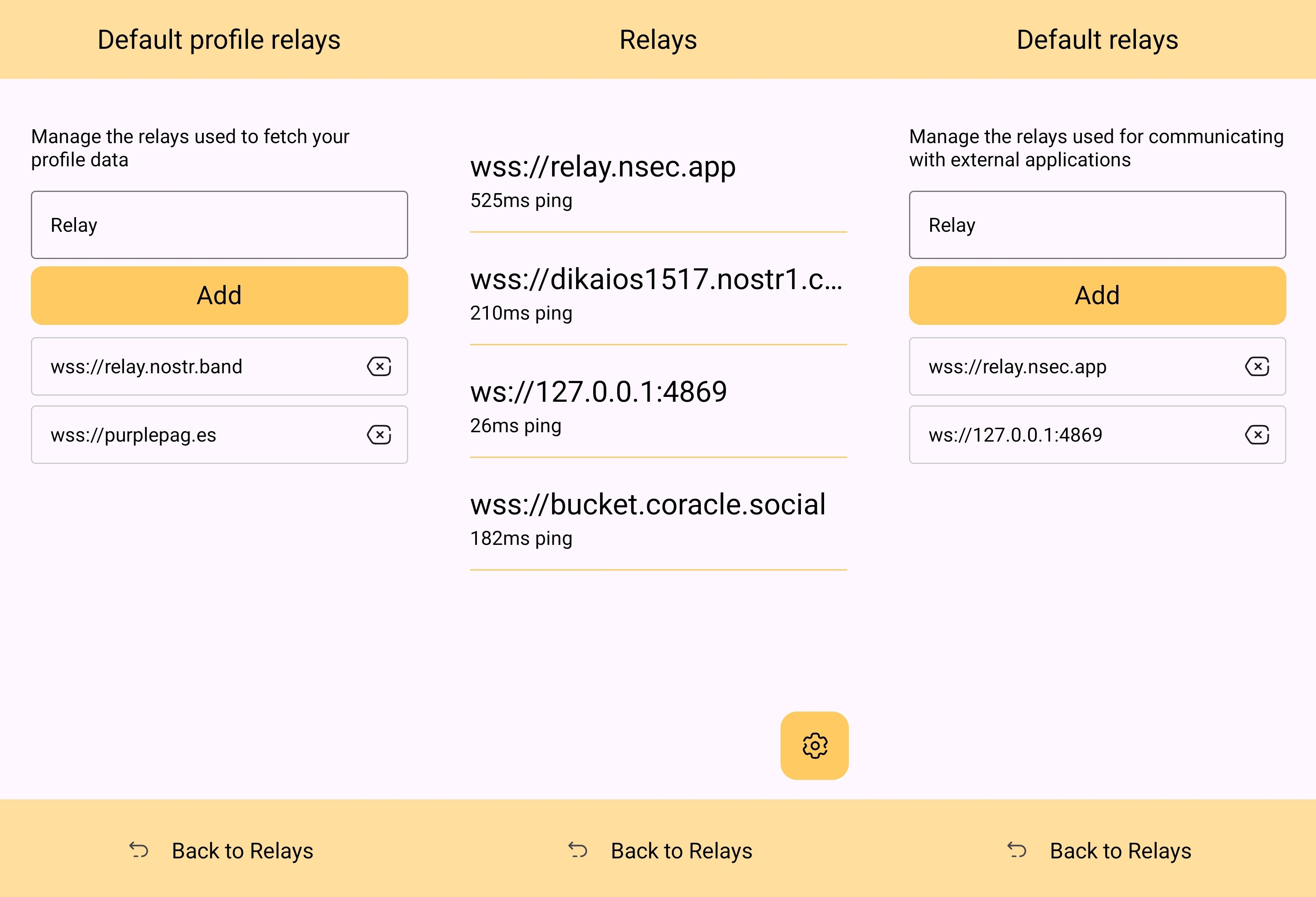
The user can also see which relays are currently connected to Amber and even look at the information that has been passed back and forth on each of those active relays. This information about actively connected relays is not only available within the application, but also in the notification that Amber has to keep in your device's notification tray in order to continue to operate in the background while you are using other apps.
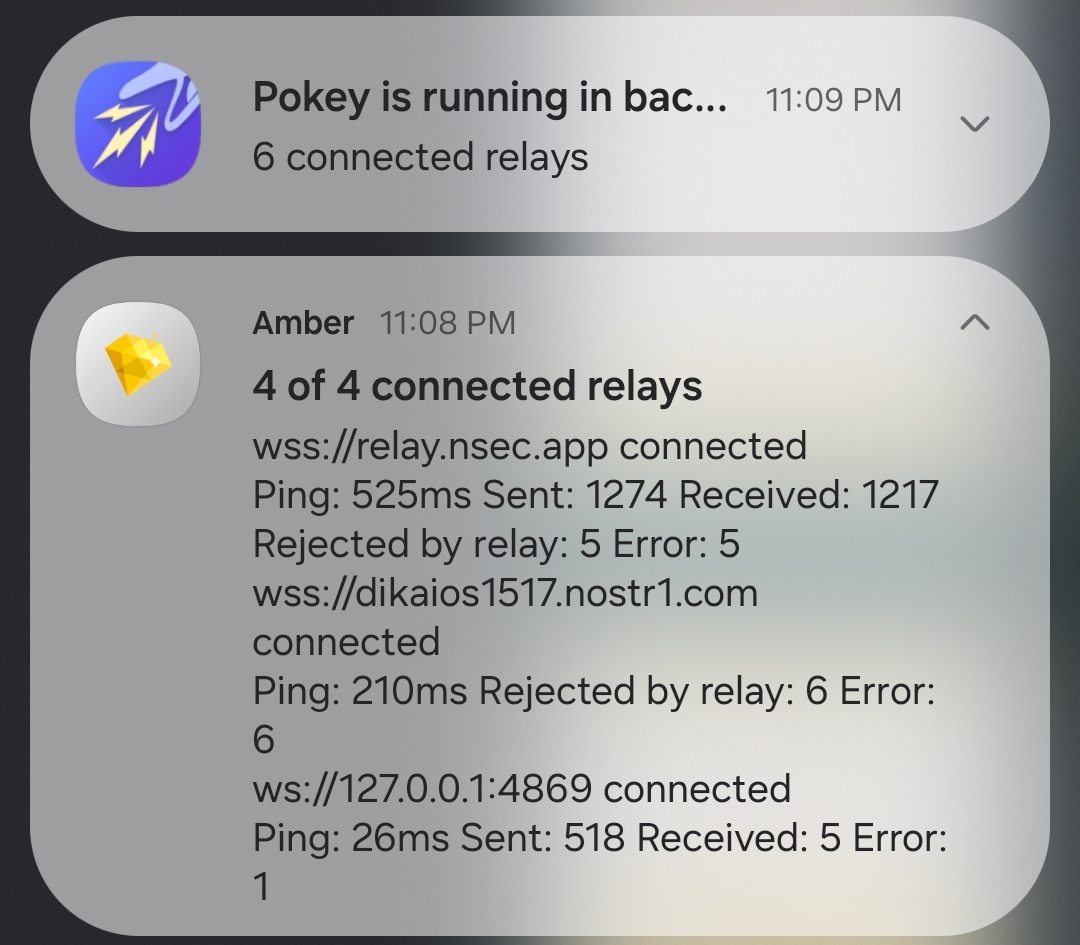
Optionality is the name of the game when it comes to how Amber handles relay selection. The user can just stick with the default signing relay, use their own relay as the default, or even use a different relay for each Nostr application that they connect to for remote signing. Amber gives the user an incredible amount of flexibility in this regard.
In addition to all of this, because not all relays accept the event types needed for remote signing, when you add a relay address to Amber, it automatically tests that relay to see if it will work. This alone can be a massive time saver, so users aren't trying to use relays that don't support remote signing and wondering why they can't log into noStrudel with the connection string they got from Amber.
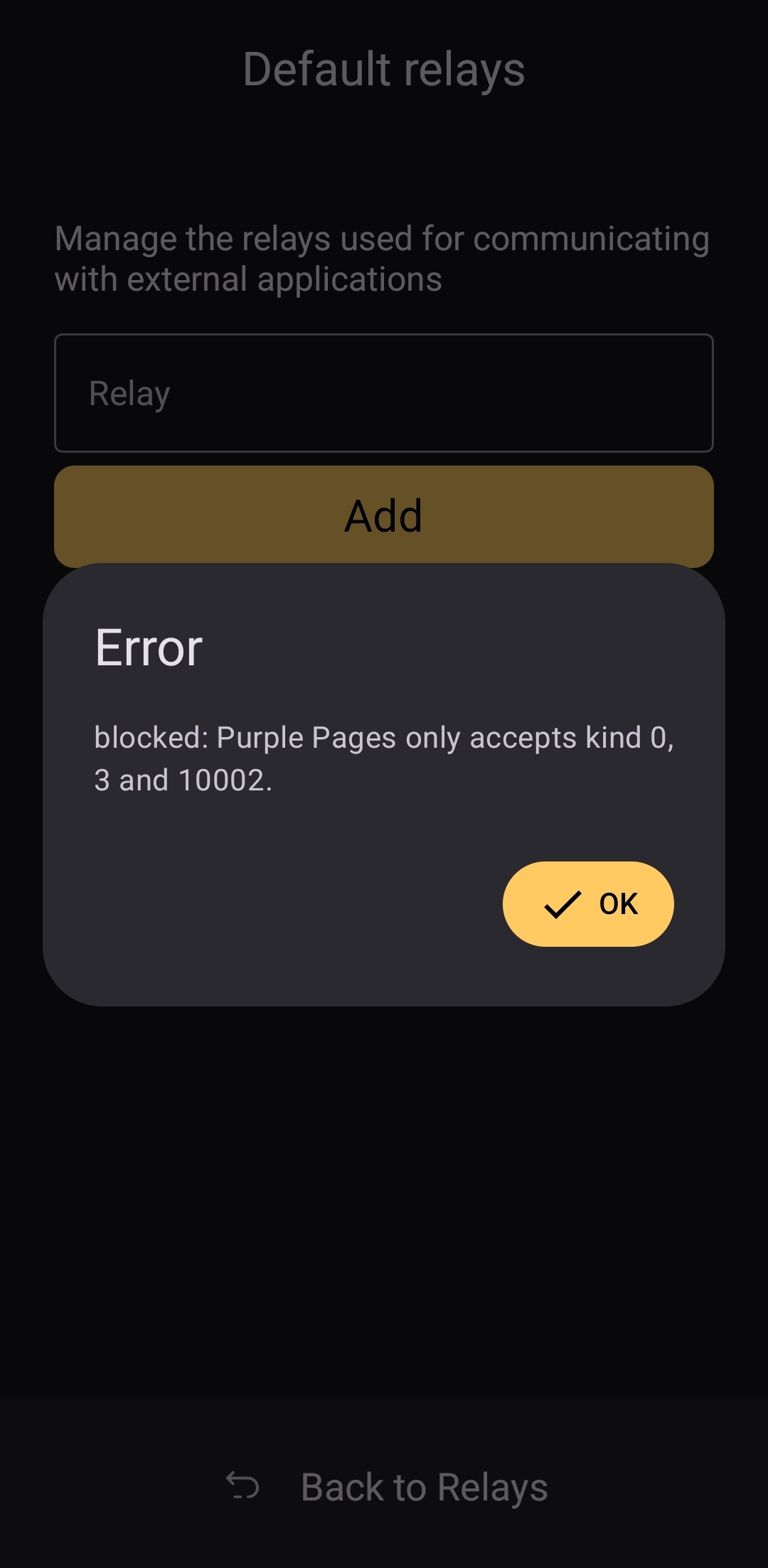
The only way I could see relay management being improved would be some means of giving the user relay recommendations, in case they want to use a relay other than relay.nsec.app, but they aren't sure which other relays will accept remote signing events. That said, most users who want to use a different relay for signing remote events will likely be using their own, in which case recommendations aren't needed.
Current Users' Questions
The AskNostr hashtag can be a good indication of the pain points that other users are currently having with any Nostr application. Here are some of the most common questions submitted about Amber in the last two months.
nostr:nevent1qqsfrdr68fafgcvl8dgnhm9hxpsjxuks78afxhu8yewhtyf3d7mkg9gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgq3qkgh77xxt7hhtt4u528hecnx69rhagla8jj3tclgyf9wvkxa6dc0sxp0e6m
This is a good example of Amber working correctly, but the app the user is trying to log into not working. In my experience with #Olas in particular, it sometimes allows remote signer login, and sometimes doesn't. Amber will receive the signing request and I will approve it, but Olas remains on the login screen.
If Amber is receiving the signing requests, and you are approving them, the fault is likely with the application you are trying to log into.
That's it. That's all the repeated questions I could find. Oh, there were a few one-off questions where relay.nsec.app wouldn't connect, or where the user's out-of-date web browser was the issue. Outside of that, though, there were no common questions about how to use Amber, and that is a testament to Amber's ease of use all on its own.
Wrap Up
If you are on Android and you are not already using Amber to protect your nsec, please do yourself a favor and get it installed. It's not at all complicated to set up, and it will make trying out all the latest Nostr clients a safe and pleasant experience.
If you are a client developer and you have not added support for NIP-55 or NIP-46, do your users the courtesy of respecting the sanctity of their private keys. Even developers who have no intention of compromising their users' keys can inadvertently do so. Make that eventuality impossible by adding support for NIP-55 and NIP-46 signing.
Finally, I apologize for the extended time it took me to get this review finished. The time I have available is scarce, Nostr is distracting, and nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 kept improving Amber even as I was putting it through its paces over the last two months. Keep shipping, my friend! You have made one of the most useful tools we have seen for Nostr to date!
Now... What should I review next?
-
 @ 2b24a1fa:17750f64
2025-04-29 08:20:58
@ 2b24a1fa:17750f64
2025-04-29 08:20:58Die Satire Muxmäuchenstill von 2004 erzählt die Geschichte des 30-jährigen Mux, der seine Mitbürgern zu mehr Verantwortungsbewusstsein erziehen möchte. Dazu stellt er Raser, Schwarzfahrer, Graffiti-Sprüher, Falschparker, Ladendiebe und Vergewaltiger, konfrontiert sie mit ihrem Verhalten und bestraft sie.
https://soundcloud.com/radiomuenchen/muxmauschenstill-x-interview-mit-jan-henrik-stahlberg?
Als Mitstreiter gewinnt er Arbeits- und Obdachlose. Mux’ fanatische Ein-Mann-Mission wächst zu einem kleinen Unternehmen. Auch privat kann er seinen Moralismus nicht zügeln und erschießt seine Freundin. Am Ende des Films wird er von einem Raser überfahren.
Ab 1. Mai läuft die Fortsetzung in den Kinos: Muxmäuschenstill X: muxfilm.de/. Nach zwanzig Jahre Wachkoma findet sich Mux in einer Welt wieder, die er nicht mehr versteht: dem wunderbaren Neoliberalismus. Wieder möchte Mux die Menschen erziehen. Doch diesmal kämpft er gegen ein System, das alles durchdringt, die Welt spaltet, unsere Lebensgrundlagen zerstört, die Reichen reicher macht und die Armen ärmer. Mux gründet den Muxismus und schart die Aussortierten des Systems um sich.
Drehbuchautor und Hauptdarsteller Jan Henrik Stahlberg führt diesmal auch Regie. Unser Autor Jonny Rieder hat mit Jan Henrik Stahlberg über seinen neuen Film gesprochen. Zunächst wollte er wissen, wo für ihn die Grenze verläuft zwischen Übergriffigkeit und Zivilcourage und wie er Mux hier einordnet.
Bild: Mux Filmproduktion
-
 @ f1f59549:f4121cfe
2025-04-28 20:26:13
@ f1f59549:f4121cfe
2025-04-28 20:26:13The function of a Zen Koan is simple; it’s like a joke — but instead of the punchline being spontaneous laughter, a Zen Koan’s punchline produces a spontaneous (but fleeting) glimpse of enlightenment.
Just like a joke, you either get it or you don’t. When someone has to explain the punchline, it loses its power.
Koans are a clever way to get around the problem that existence and all meaning derived from it are completely ineffable. Zen acknowledges that attempting to explain "universal truths" is a paradox within itself — the moment you try to define it, you’ve already lost it.
The clever device of a koan is that it manages to get around this paradox by pointing towards enlightenment rather than directly at it.
Universal truths, by definition, are incomprehensible and cannot be explained through intellectual discussion. While other philosophies attempt to explain the nature of existence through logic and reason, Zen acknowledges that the true nature of reality is beyond words and avoids this conceptualization completely.
Am I a terrible Zen student for spending most of my time intellectualizing the crap out of Zen concepts like this anyway — Mu!
What is a Koan?
“The role of the koan is not to lead us to Satori (enlightenment), but on the contrary, to make us lose our way and drive us to despair." — Philip Kapleau.
Zen Koans are paradoxical short stories, dialogues, or questions designed to break the logical mind, disrupt habitual thinking, and provoke direct experience (Kenshō).
They often feature a wise master who does something completely unexpected or illogical.
Some use metaphors to hint at deeper truths.
Others rely on questions that are simply unanswerable.
Ultimately, these stories don’t provide any answers to the reader — at least, not in the traditional sense. Instead, they act as a mirror reflecting the mind's attachments and delusions — helping to bring our unconscious biases into view and flip them on their head. This process dismantles our conditioned thought patterns and erodes the rigid structures of our ego that prevent us from seeing things clearly.
It's difficult to explain the purpose of Zen Koans without sounding like a walking contradiction — so let's explore some of their central themes, briefly examine their history, and then dig into a few of the most famous Zen koans.
The Sound of One Hand Clapping
This is probably the shortest Zen koan in existence — it consists of a simple question:
"You know the sound of two hands clapping — now tell me, what is the sound of one hand clapping?"
This koan likely originated from Hakuin Ekaku (1686–1769), a Japanese Rinzai Zen master who revived the use of koans in Zen practice. At the time, most Zen being practiced in Japan had become formalized and ritualistic. Many monks treated koans as intellectual puzzles rather than tools for direct experience.
Hakuin wrote a series of koans designed to break this type of thinking by forcing students to confront the limits of rational thought.
This koan is one of the first breakthrough koans given to students to push them beyond dualistic thinking.
We know that two hands clapping makes a sound (duality), but there is no way to explain or conceptualize the sound of just one hand clapping (non-duality).
Do What's Next
A student came to his teacher — “I want to learn & become enlightened. Please teach me.”
> The teacher asked — “Have you eaten your porridge?”*
> The student replied — “I have eaten.”*
> The teacher said — “Then you better go wash your bowl.”*
> At that moment, the student was enlightened.*
This koan is an example of how even the mundane holds the key to awakening if we can see things with clarity. The student comes to the master expecting him to drop some deep wisdom about attaining enlightenment — but the master denies this from him and chooses instead to focus on the simple, immediate task of washing his bowl.
Zen koans like this teach us that enlightenment isn’t some distant, mystical achievement — it’s found in all the ordinary, mundane moments of our lives.
This is it. Life is happening right now. There's no "higher state" to be achieved through striving or accumulation of knowledge.
It echoes the old Zen adage:
"Before enlightenment, chop wood, carry water. After enlightenment, chop wood, carry water."
4 Monks
Four monks decided to meditate silently without speaking for two weeks. They lit a candle as a symbol of their practice and began. By nightfall on the first day, the candle flickered and went out.
> The first monk said — “Oh, no! The candle is out.”*
> The second monk said — “We’re not supposed to talk!”*
> The third monk said — “Why must you two break the silence?”*
> The fourth monk laughed and said — “Ha! I’m the only one who didn’t speak.”*
At first glance, this koan appears to be a simple story of monks breaking their vow of silence — but the meaning goes much deeper than that.
This koan is a lesson of attachment — but not in the typical obvious, material sense you might expect. Zen teaches non-attachment of all things — material objects, rules, and ideas (including Zen itself).
The first monk was attached to the candle — when it went out, he was unable to stay silent.
The second monk was attached to the rule of silence — when it was broken, he was unable to stay silent.
The third monk was attached to judging others — when he saw the other two monks fail, he was unable to stay silent.
The fourth monk was attached to pride — when he thought he "won," he was unable to stay silent.
The Blind Man
Late one night, a blind man was about to go home after visiting a friend — "Please," he said to his friend, "May I take your lantern with me?"
> "Why bother with a lantern?" — asked his friend — "You won't see any better with it."*
> "No," — said the blind man — "perhaps not. But others will see me better and won’t bump into me.”*
> So his friend gave the blind man the lantern. It was made of paper and bamboo and held a fresh wax candle inside.*
> Off went the blind man with the lantern, and before he had gone no more than a few feet, Crack! Someone walked right into him.*
> The blind man was very angry.*
> "Why don't you look out?" — he stormed — "Can’t you see this lantern I’m carrying?!"*
> The stranger looked at the man for a moment — "Why don't you light the candle?"*
This koan exposes the perils of making assumptions and reveals the limits of perception. The blind man believes that carrying the lantern will prevent people from bumping into him — but he never actually confirms the candle is lit in the first place.
It's a lesson in self-awareness, humility, and the danger of unexamined beliefs. It’s easy to blame others when things go wrong rather than examining our own assumptions.
It begs the question: Who is truly blind? The man who cannot see? Or the one who assumes he is being seen?
More Zen Koans
I'm a huge fan of koans. I think they're an excellent method to help us dismantle our preconceived notions about the world, the self, and our perception of reality.
They're short, high-impact ponderings that help us question what we know to be true and force us to abandon logic and binary reasoning.
So, for the next few months, I'm going to send a fresh Zen koan to your inbox every Thursday.
I acknowledge that in this post, I acted hypocritically by providing you with my interpretations of a few example koans. My intention was to help you visualize and understand how a koan functions and why they’re so useful to us as students of Zen — however, many Zen teachers argue that presenting an interpretation of the possible meanings of a Zen koan reduces it to an intellectual exercise — which, of course, is the exact opposite of its true purpose.
For this reason, the koans I send each week will be devoid of any interpretation.
Alan Watts, author of the book The Way of Zen — one of the greatest Western interpreters of Zen thought and the master at explaining the unexplainable — argued that if Zen had no secrets, there's no harm in articulating its ideas. I tend to agree with this perspective but argue that reading (and writing) about Zen is in no way the same as practicing Zen. A koan’s true impact comes from direct experience, and much of its power is diminished when it’s filtered through someone else’s interpretation.
For me, koans are a way to engage with the Zen path — helping to disrupt our thoughts and point us toward a more experiential Zen practice.
Instead of looking for meaning in these koans, I invite you to sit with them. Don’t try to solve them. Don’t try to explain them. If they frustrate you, let them frustrate you. If they make you laugh, let them make you laugh. If they do nothing for you, shrug, take a deep breath, and move on with the rest of your day.
Subscribe to The Zen Psychedelic
Thanks for reading The Zen Psychedelic! Consider subscribing for free to receive new posts and support my work.
You can subscribe here using Nostr or follow me on Substack.
→ This post was originally published on The Zen Psychedelic Substack
-
 @ a1d36df6:a3b9f5a0
2025-04-29 08:02:33
@ a1d36df6:a3b9f5a0
2025-04-29 08:02:33Originally written in: November 2024
"Show me the incentives, and I'll show you the outcome"[^mungerquote].
"Even bacteria respond to motivation." ~[^dufrene2020][^amoedo2024].
Introduction
In Austrian economics, time preference refers to the value individuals place on present consumption versus future consumption [^rothbard1993man]. A society with a lower time preference is more inclined to save, invest, and plan for the long term, thereby fostering progress and stability [^ammous2018]. In contrast, a society with a higher time preference tends toward immediate consumption rather than investment — or invests without a true understanding of its purpose — leading to short-term planning and a gradual drift from foundational societal values, traditions, and culture [^hoppe2001].
The definition of investment is the process of allocating resources to productive activities, prioritizing future gains over immediate consumption. It involves capital accumulation and is key to economic growth, as individuals delay gratification to increase future value. This approach underlies capital formation and enhances an economy's production capacity, aligning with lower time preference and fostering long-term prosperity [^mises1998].
With a foundational understanding of time preference and investment, we can begin to examine what motivates people today. Given the prevalence of high time preference in modern society, the government can capitalize on this tendency by offering immediate handouts and benefits, satisfying the population's desire for instant gratification, often at the expense of long-term prosperity and future gains. This tendency is also mirrored in mainstream media, where a focus on sensational, attention-grabbing stories diverts focus from deeper, structural issues. By amplifying polarizing narratives [^gentzkow2006media], often tied to social identity or lifestyle differences, the government and media create a cycle of constant engagement and distraction, steering public attention towards short-term controversies and away from underlying economic or social policy issues [^caplan2001rational].
Debt & Fractional-Reserve Banking
A common denominator that repeatedly emerges in such destructive behavior promoted by governments is the issue of money. As money drives the world, understanding and following its flow not only reveals how it operates but also uncovers those who wield control over it, and how human behavior is driven by it.
Money is a broad term encircling all assets that can be used for exchange, storage, and valuation, covering both physical and digital forms [^ammous2023]. Cash is a subset of money, referring specifically to physical currency, such as coins and notes.
The process of money creation, typically managed by governments and central banks, is the foundation of economic dependency within the financial system. In most economies, central banks control currency creation through mechanisms like open market operations and debt. For instance, when a central bank, such as the Federal Reserve, issues new currency, it does so by purchasing government securities from commercial banks, thus adding currency to the economy. However, this transaction is not debt-free; it obliges the government to repay the borrowed amount with interest.
In common words, the process of creating money is as follows: the government request to the central bank a certain amount of money to be printed in borrowing form. The central bank then creates that money, out of thin air, on the promise that the government will repay the central bank down the road. Since the government does not produce anything, in order to repay the central bank, the government then sells the debt via bonds to anyone who would like to buy the government debt. In even more simple words: the government and central bank creates money out of thin air based on debt [^ammous2021].
The issue with money creation is not only by the fact that it was created out of thin air, but because money creation has other issues tied to it: the debt, the creation of fractional-reserve monetary system, inflation, and interest.
This foundational reliance on debt, since it is present in the very beginning of money creation, renders the entire monetary system debt-dependent. Therefore, saving and investing within such a system becomes questionable, as the system's nature opposes the principles of sustainable wealth accumulation, thus leading human behavior not to save but to spend.
A fractional-reserve monetary system is a banking structure in which banks retain only a small fraction of their depositors' funds — historically around 10%, but today often as low as 1% [^bundesbank2024] — while lending out or investing the remainder. This setup allows banks to expand the money supply and stimulate economic activity through a process known as deposit expansion [^federalreserve1975modern]. Deposit expansion occurs when banks effectively treat a portion of deposited funds as new money, multiplying the original deposit base. For example, if a bank holds deposits totaling 1 million euros, it can lend out up to 1.9 million euros, as long as it maintains 10% of the initial deposit in reserve. This cycle can repeat, enabling banks to increase the total money supply to infinity, but the "Modern Money Mechanics: A Workbook on Bank Reserves and Deposit Expansion" and government applying it recommends not doing it above 9 times the original deposit value [^federalreserve1975modern].
To make matters worse, inflation and interest exacerbate the problems inherent in this monetary system. Interest is a foundational element of the system, initially intended to address the original debt incurred by the government. In economic terms, interest represents the "price" of time preference, a premium placed on present goods over future goods. To illustrate the impact of interest, consider the cost of a house in today's system: a house priced at 500,000 euros with a 4% variable interest rate ends up costing around 860,000 euros over 30 years, with 360,000 euros paid in interest alone.
Inflation, on the other hand, is the increase in the money supply — money printing — and can only be truly calculated by M2[^1] money supply metric. Inflation erodes the value of both assets and earned income, as each new unit of currency devalues existing money. This devaluation impacts not only the purchasing power of savings but also the real cost of goods and services over time, reducing the long-term value of assets people believe they own.
The government
Operating within a monetary system stretched beyond its limitations, the government faces the dual challenges of controlling inflation and satisfying its growing spending demands. To fund its expenditures, the government often provides public benefits — subsidies, "free" healthcare, public transport, security, military, and welfare in general — to justify continual spending and cultivate public support - via voting, in most democratic countries.
Welfare and most government programs redistribute wealth from producers to non-producers, fostering dependency on the state. Over time, this erodes individual sovereignty and expands government control, restricting freedom, and reducing people to slaves or cash cows.
The government justifies taxes as payment for welfare and public services, but also claims they curb inflation by reducing the need to print money. The logic is that by reclaiming taxpayer money, the money supply is controlled. However, this is misleading, especially when the government can print money at will, making taxation on such currency inherently flawed.
Taxes are extracted via coercion - violence - by the government onto the population. The government then decides where to allocate this money, based on their guess of what the population needs, excluding private preferences. Therefore, taxes are not an incentive to accumulate, not even to work more. Taxes are an incentive to do right the opposite: do not save and do not work more.
Another tactic the government employs is to create crises that it alone can "solve", thus requiring more taxes or funding. Recent examples include crises like COVID-19, the "green" agenda, and initiatives to combat climate change[^2]. In each case, the government presents itself as the sole solution, yet solving these crises inevitably demands additional resources — in the form of increased taxation.
Even minimal critical thinking would prompt one to question the true necessity of taxes in a government that owns and controls the money printer. Given what we now understand, if you were in the government's position, would you willingly relinquish control of money creation by tying it to something like gold, empowering people to become smarter, independent, and wealthy?
The government, through various channels — media, education, propaganda, welfare, and government subsidies — ensures that people remain obedient and uninformed. It keeps them financially constrained by increasing taxes and imposing extensive regulations, while fostering dependency through handouts, welfare, and other social programs. The government is the only entity that, by law, can use violence and coercion without prosecution [^rothbard2009].
"Anyone who, although human, is by nature not yours but someone else's"[^ambler1987].
It is therefore unsurprising that many live in a state akin to enslavement, reflecting a mindset shaped by constant dependency. It is no wonder that people are discouraged from having children, as they can barely support themselves. Nor is it surprising that individuals might question the need to continue their bloodline, believing in the illusory value of "fake money" [^kiyosaki2019] and trusting present "investments" and the government to provide a pension in old age. And it's certainly not surprising to see people asking the government for solutions to every problem, when the government leaves them no viable alternatives.
"Show me the incentives, and I'll show you the outcome"[^mungerquote].
That statement serves as a powerful tool for understanding and addressing complex issues. When observing behaviors that may appear unusual — such as individuals identifying as "trans-species," a phenomenon linked to mental health concerns [^pinna2022] — it's essential to consider the underlying incentives. Who benefits most from a society in which individuals remain financially constrained, dependent, and uninformed? A fiat-based monetary system functions as a modern form of economic control, keeping people poor by design. Taxes, effectively a penalty for productivity, contrast sharply with welfare programs, which often reward dependency and reinforce reliance on the government. Meanwhile, government narratives and selective information shape public beliefs, protecting institutional interests and discouraging critical inquiry[^3].
Conclusion
Like the fungus that infects in parasitic way an ant's nervous system - Ophiocordyceps Unilateralis -, rendering it a zombie [^britannica2024] controlled by an external force, similarly, modern bureaucracies exploit the mechanisms of fiat money, debt, and taxation [^rothbard2009] to maintain control over individuals, steering them away from self-reliance and critical thinking toward a state of perpetual dependence.
The parallels are striking: just as the fungus manipulates the ant's behavior to secure its reproduction, governments manipulate public perception, creating crises, shaping incentives, and fostering dependence[^rothbard2009] through welfare programs[^caplan2001rational], inflated debt[^ammous2018], and coercive taxation. These mechanisms suppress individuality, reduce productivity, and shift power further into centralized hands[^gentzkow2006media], leaving citizens "zombified", detached from purpose and independence.
"Even bacteria respond to motivation."[^dufrene2020]
If tolerated — even by you, dear reader — this parasitic cycle will continue to erode humanity's dignity and potential. The solution lies in reclaiming agency by building a society grounded in sound money, meaningful productivity, and spiritual and cultural foundations that connect us to higher purposes. As warned in Jeremiah 17:5 [^4], trusting fallible human systems leads to enslavement. True freedom comes from rejecting exploitative bureaucracies and embracing systems aligned with truth, autonomy, and resilience.
Another way is to fully understand the system and opt out. This requires mastering the rules and using them to your advantage. If legal avenues exist to avoid taxation, expropriation, eminent domain, or government coercion, then the first step is to change the game for yourself.
The monetary system and government incentives shape human behavior, influencing those who allow themselves to be controlled by them.
fiat #bitcoin #austrian-economics #freedom #slavery #money #government #antipropaganda #propaganda #taxes #tax #greenagenda #wef #who
Footnote
[^1]: M2 refers to savings deposits + money market mutual funds + small time deposits. M2 includes all of M1 plus "near money" (M0), which consists of savings deposits, money market accounts, and small-denomination time deposits (like certificates of deposit under a certain amount). M2 is commonly tracked by central banks to gauge medium-term economic activity and savings behavior, as it includes money that people save rather than spend immediately.
[^2]: Since the 1990s, societies worldwide have been confronted by a series of global crises, often framed as urgent and overwhelming challenges. All scams. Including deforestation, ocean and air pollution, nuclear waste, oil spills, plastic and soil pollution, drought, fossil fuel consumption, rising sea levels, species extinction, extreme weather, global warming, melting glaciers, acid rain, and, recently, climate change. Each crisis has shaped public opinion and policy, and also created new laws, regulations, and taxes.
[^3]: Politicians are merely psychopath[^hareleonmayersalinasfolino2022][^klaas2023] parasites.
[^4]: Cursed is the one who trusts in man, who draws strength from mere flesh and whose heart turns away from the Lord.
References
Bibtex
bibtex @book{ammous2018, title={The Bitcoin Standard: The Decentralized Alternative to Central Banking}, author={Ammous, Saifedean}, year={2018}, publisher={Wiley}, url={https://saifedean.com/tbs} } @book{ammous2023, author = {Saifedean Ammous}, title = {Principles of Economics}, year = {2023}, publisher = {Saifedean Ammous}, address = {Self-published}, url = {https://saifedean.com/poe} } @book{ammous2021, author = {Saifedean Ammous}, title = {The Fiat Standard: The Debt Slavery Alternative to Human Civilization}, year = {2021}, publisher = {Wiley}, address = {Hoboken, NJ}, url = {https://saifedean.com/tfs} } @book{rothbard1993man, author = {Murray N. Rothbard}, title = {Man, Economy, and State: A Treatise on Economic Principles}, year = {1993}, publisher = {Ludwig von Mises Institute}, address = {Auburn, Alabama}, note = {Originally published in 1962}, url = {https://mises.org/library/man-economy-and-state-power-and-market} } @book{hoppe2001, author = {Hans-Hermann Hoppe}, title = {Democracy: The God That Failed: The Economics and Politics of Monarchy, Democracy, and Natural Order}, year = {2001}, publisher = {Transaction Publishers}, address = {New Brunswick, NJ}, url = {https://mises.org/library/democracy-god-failed} } @book{mises1998, author = {Ludwig von Mises}, title = {Human Action: A Treatise on Economics}, year = {1998}, publisher = {Ludwig von Mises Institute}, address = {Auburn, Alabama}, note = {Originally published in 1949}, url = {https://mises.org/library/human-action-0} } @article{gentzkow2006media, author = {Matthew Gentzkow and Jesse M. Shapiro}, title = {Media Bias and Reputation}, journal = {Journal of Political Economy}, volume = {114}, number = {2}, pages = {280-316}, year = {2006}, publisher = {University of Chicago Press}, url = {https://doi.org/10.1086/499414} } @article{caplan2001rational, author = {Bryan Caplan}, title = {Rational Irrationality and the Microfoundations of Political Failure}, journal = {Public Choice}, volume = {107}, number = {3}, pages = {311-331}, year = {2001}, publisher = {Springer}, url = {https://doi.org/10.1023/A:1010349129605} } @book{federalreserve1975modern, author = {{Federal Reserve Bank of Chicago}}, title = {Modern Money Mechanics: A Workbook on Bank Reserves and Deposit Expansion}, year = {1975}, publisher = {Federal Reserve Bank of Chicago}, url = {https://archive.org/details/modern-money-mechanics/mode/2up} } @misc{bundesbank2024, author = {{Deutsche Bundesbank}}, title = {Minimum Reserves}, year = {n.d.}, url = {https://www.bundesbank.de/en/tasks/monetary-policy/minimum-reserves/minimum-reserves-625912}, note = {Accessed: 2024-11-07} } @article{ambler1987, author = {Wayne Ambler}, title = {Aristotle on Nature and Politics: The Case of Slavery}, journal = {Political Theory}, volume = {15}, number = {3}, pages = {390-410}, year = {1987}, month = {Aug.} } @book{kiyosaki2019, author = {Robert T. Kiyosaki}, title = {FAKE: Fake Money, Fake Teachers, Fake Assets: How Lies Are Making the Poor and Middle Class Poorer}, year = {2019}, month = {April}, publisher = {Plata Publishing}, address = {Scottsdale, AZ}, note = {Paperback, Illustrated Edition} } @article{hareleonmayersalinasfolino2022, title = {Psychopathy and crimes against humanity: A conceptual and empirical examination of human rights violators}, journal = {Journal of Criminal Justice}, volume = {81}, pages = {101901}, year = {2022}, issn = {0047-2352}, doi = {https://doi.org/10.1016/j.jcrimjus.2022.101901}, url = {https://www.sciencedirect.com/science/article/pii/S0047235222000216}, author = {Robert D. Hare and Elizabeth León-Mayer and Joanna Rocuant Salinas and Jorge Folino and Craig S. Neumann}, keywords = {Crimes against humanity, Human rights violators, Terrorism, Psychopathy, PCL-R, SRP-SF, Four-factor model, Latent profile analysis}, abstract = {Purpose There is a dearth of empirical data on the contributions of personality, psychopathology, and psychopathy to terrorism and its actors. Because of a fortuitous set of circumstances, we had access to a sample of men convicted of crimes against humanity (CAH) committed during the Pinochet regime, each rated by expert clinicians on the Psychopathy Checklist-Revised (PCL-R). We also had PCL-R ratings for samples of general offenders and community participants. Methods We determined the psychometric properties of the PCL-R for these samples, performed structural equation modeling (SEM) to investigate the factor structure of the PCL-R, and conducted a latent profile analysis (LPA) of the obtained factors to identify classes or subtypes within the samples. Results The PCL-R's psychometric properties and factor structure were in accord with findings from other countries and settings. The PCL-R total scores of the CAH and general offenders were virtually the same but much higher than those of the community sample. However, the CAH group had extraordinarily high scores on the Interpersonal/Affective facets yet relatively low scores on the Lifestyle/Antisocial facets. LPA identified the expected four latent classes, with most CAH men located within the Callous-Conning class. Conclusions The results of this study provide unique information about the psychopathic propensities of a sample of state violators of human rights. Their pattern of PCL-R scores was consistent with an extreme disposition for self-serving, callous, and ruthless treatment of others, without guilt or remorse, and in the absence of a prior documented history of severe antisocial behavior.} } @misc{klaas2023, author = "{Brian Klaas}", title = "{{How many politicians are psychopaths?}}", howpublished = {\url{https://www.forkingpaths.co/p/how-many-politicians-are-psychopaths}}, note = {Online; accessed 29 January 2024}, year=2023 } @article{pinna2022, title={Mental health in transgender individuals: a systematic review}, author={Pinna, Federica and Paribello, Pasquale and Somaini, Giulia and Corona, Alice and Ventriglio, Antonio and Corrias, Carolina and Frau, Ilaria and Murgia, Roberto and El Kacemi, Sabrina and Galeazzi, Gian Maria and others}, journal={International Review of Psychiatry}, volume={34}, number={3-4}, pages={292--359}, year={2022}, publisher={Taylor \& Francis}, doi={10.1080/09540261.2022.2093629}, url={https://pubmed.ncbi.nlm.nih.gov/36151828/} } @book{rothbard2009, title={Anatomy of the State}, author={Rothbard, Murray}, year={2009}, publisher={Ludwig von Mises Institute} } @misc{britannica2024, author = {{Encyclopaedia Britannica}}, title = {Zombie-Ant Fungus}, year = {n.d.}, url = {https://www.britannica.com/science/zombie-ant-fungus}, note = {Accessed: 2024-11-07} } @misc{amoedo2024, author = {Renato Amoedo}, title = {Até as bactérias respondem a uma motivação}, year = {2024}, note = {Famosa frase mencionada em entrevistas e podcasts relacionados a comportamento e motivação}, howpublished = {Comentário público}, } @article{dufrene2020, title={Mechanomicrobiology: how bacteria sense and respond to forces}, author={Dufrêne, Yves F. and Persat, Alexandre}, journal={Nature Reviews Microbiology}, volume={18}, pages={227--240}, year={2020}, month={April}, doi={10.1038/s41579-019-0314-2}, url={https://doi.org/10.1038/s41579-019-0314-2}, publisher={Springer Nature}, note={Accepted 06 December 2019, Published 20 January 2020} } @misc{mungerquote, author = {Munger, Charlie}, title = {Show me the incentive and I will show you the outcome}, note = {Often attributed to Charlie Munger, known for his wisdom on finance and life as Warren Buffett's business partner.}, howpublished = {Quote}, year = {n.d.}, url = {https://elevatesociety.com/quotes-by-charlie-munger/} } -
 @ 401014b3:59d5476b
2025-04-22 00:23:24
@ 401014b3:59d5476b
2025-04-22 00:23:24About Me
I come to Nostr with extensive experience in the digital landscape. As a blockchain native since 2017, I've witnessed the evolution of decentralized technologies firsthand. Most of my professional career has been spent working within big tech companies, giving me a unique perspective on both centralized and decentralized systems.
My social media journey began on Twitter in 2007, where I've maintained a presence for over 17 years. I've also explored other decentralized social platforms including BlueSky, Farcaster, and Lens Protocol. As a Bitcoin maximalist, I was particularly intrigued by Nostr's compatibility with the Lightning Network, which initially drew me to the platform.
The Onboarding Challenge
The Nostr onboarding experience presents a significant hurdle for newcomers. Despite my technical background in blockchain technologies, I found the initial setup process more complicated than expected. Understanding public/private key cryptography just to join a social network creates a steeper learning curve than necessary.
BlueSky and Farcaster have demonstrated that it's possible to maintain decentralized principles while providing a more streamlined onboarding experience. Their approaches show that user-friendly design and decentralization aren't mutually exclusive concepts.
Relay Management: Room for Improvement
The concept of relays represents one of Nostr's most distinctive features, though it can be confusing for newcomers. While many clients come pre-configured with default relays, users eventually encounter situations where content or connections seem inconsistent.
When someone I've interacted with doesn't appear in my feed or doesn't respond, I'm often left wondering if we're simply on different relays. This uncertainty creates friction that doesn't exist on other platforms where connectivity is handled behind the scenes.
The relay system introduces a layer of complexity that, while important to Nostr's architecture, could benefit from better abstraction in the user experience. When using BlueSky or Farcaster, I don't need to think about the underlying infrastructure, something Nostr could learn from while maintaining its decentralized principles.
The Zap Economy: Growing Pains
The Lightning-powered zap system shows tremendous potential, but I've observed some concerning economic patterns. Longer-term Nostr users have expressed frustration about continuously sending zaps while seeing limited growth in the overall ecosystem.
Interestingly, there appears to be a connection between this liquidity issue and community growth dynamics. Some established users who voice concerns about bearing the financial burden of the zapping economy are simultaneously less welcoming to newer accounts, rarely following, engaging with, or zapping newcomers.
This creates a challenging environment for new users, who face a cold reception and have little incentive to load their Lightning wallets or participate in the zap economy. Why bring fresh liquidity to a platform where established users rarely engage with your content? This dynamic has limited the expansion of the ecosystem, with the same sats often circulating among established users rather than growing with new participants.
Client Diversity: Strength and Challenge
Nostr's multiple client options offer users choice, which is valuable. However, the implementation of NIPs (Nostr Implementation Possibilities) varies across clients, creating inconsistent experiences. Features that work seamlessly in one client might be implemented differently in another.
This extends to fundamental aspects like search functionality, thread navigation, and notification systems, all of which can differ significantly between clients. For users accustomed to consistent experiences, this fragmentation creates a learning curve with each new client they try.
Lightning Integration: Varying Experiences
The Lightning Network integration varies in quality and user experience across Nostr clients. While the functionality is generally present, the implementation quality, feature set, and ease of use differ depending on which client you choose.
This inconsistency means users may need to experiment with several clients to find one that provides the Lightning experience they're looking for, rather than having a consistent experience across the ecosystem.
Finding Balance
Nostr appears to be navigating the challenge of balancing technical innovation with user experience. While its cryptographic foundation and decentralized architecture are impressive technical achievements, these same strengths sometimes come at the cost of accessibility.
Despite my technical background and interest in decentralized technologies, I find myself using BlueSky and Farcaster more frequently for daily social interactions, while checking Nostr less often. For Nostr to achieve its potential for broader adoption, addressing these user experience considerations while maintaining its core principles will be essential.
The platform has tremendous potential with improvements to user experience, community dynamics, and economic sustainability, Nostr could evolve from a fascinating technical experiment into a truly compelling alternative to mainstream social media.
-
 @ f1f59549:f4121cfe
2025-04-28 20:21:28
@ f1f59549:f4121cfe
2025-04-28 20:21:28Ego is a fundamental part of the human condition. It provides us with the necessary ability to separate and compartmentalize ourselves from the rest of the world.
Our ego allows us to exist in the chaos of existence.
The spiritual path is seen as a way to “escape the ego” and achieve a higher state of consciousness. A state where the confines of the ego no longer hold us back from seeing things as they are and allow us to experience true bliss.
But there’s a paradox to this whole process.
By seeking spiritual advancement, we have to accept that there is something to improve and someone to do the improving.
This suggests that this improvement somehow makes us better than someone who has not achieved similar levels of improvement.
This kind of thinking is inherently egotistical.
As we advance down the spiritual path — escaping the grasp of ego and removing attachments — spirituality itself can end up feeding the ego. Most of the time, we don’t even notice it while it’s happening.
It’s an unconscious process that develops along the way. Only after we notice it within ourselves can we course-correct.
I acknowledge that writing this article is itself an example of spiritual egotism.
Who am I to talk about dissolving the ego? What are my goals for writing this piece? By pointing out the hypocrisy behind having spiritual convictions or goals, am I in some way suggesting myself to be free from these convictions?
I am in no way exempt from the clutches of spiritual egotism — I certainly have not reached enlightenment.
But the paradox is that if I had, I probably wouldn’t be talking about it now.
This is known in Buddhism as the “noble silence.”
The only way to understand what it truly means to “dissolve the ego” is by discovering it spontaneously. It is not something that can be taught.
This is the approach Zen Buddhism takes to reach enlightenment. By accepting that the truth cannot be told, the master does not try to speak it. Instead, the master simply pops the ego of his students as it bubbles up from time to time.
This employs a concept called “the middle way.”
You know that you must dissolve your ego. But you can’t, so trying it is also pointless. The middle way says, “I will do my best to escape my ego, but I accept that I will fail.”
One thing we can do is pay attention to our failings. When you perform a kind act for another person, consider the motivation behind why you did it. Was it for their sake or for yours?
If you’re able to convince yourself these acts come from selfless motives — take notice — your ego has just presented itself.
The Paradox of Spiritual Development
You want to improve yourself by changing your consciousness. But the self that needs to be improved is the same one doing the improving.
This is a paradox.
As egotistical beings, we cannot be without ego.
At its core, the very reason one seeks to dissolve the ego is to improve oneself. Whether it’s to feel well, perform more effectively, or improve relationships with others — the very desire to achieve this improvement is egotistical.
This forms a negative feedback loop. The more we attempt to remove the ego, the more egotistical we become.
Essentially, the harder we try to avoid it, the more we become it.
By choosing to take a path toward enlightenment — we can not reach enlightenment.
The great Alan Watts says it best (paraphrasing):
“As long as you think and feel that you are contained in your bag of skin, there is no way whatsoever to behave unselfishly. You can imitate unselfishness. Undergo all kinds of highly refined forms of unselfishness. But you’re still tied to the gold chains of your good deeds.”
Is There A Solution?
Not exactly, but we may be able to move closer toward enlightenment by accepting its impossibility. Simply allowing ourselves to notice this paradox in ourselves may allow us to redirect course toward the middle path once again.
Let’s look at the story of the Buddha as an example.
Siddhartha was an ascetic for several decades. Acetics of the time would do all sorts of austere techniques. He would starve himself, sleep out in the cold, and purposely subject himself to discomfort and hardship — all an attempt to dissociate from his physical body and, thus, his ego.
The goal was to “reach” enlightenment.
But all the attempts the Buddha made to get himself out of the trap failed.
Siddhartha only achieved enlightenment when he realized that the trap and the trapped are one. By this realization, there isn’t any trap left.
He realized that the spiritual journey isn’t about being on some sort of “higher level.” There is no “end goal” or plateau to reach.
The spiritual teacher Eckhart Tolle puts it another way:
“The ego has many ideas. It says, ‘I want to be a spiritual person. I want to be recognized as a spiritual person. I want to be more spiritual than all these people. And I’m definitely more spiritual than you… The essential dysfunction of the ego is still operating. This is why we have the phrase ‘the road to hell is paved with good intentions’… You have to reach the place within yourself that is unconditioned; that is what I sometimes call formless.”
Spiritual Arrogance is a Blind Spot on the Path to Enlightenment
Spirituality can help you release the firm grasp your ego has over you, but it can also reinforce it.
Spiritual arrogance arises when someone develops an identity about seeking a path to enlightenment. It’s sometimes referred to as “spiritual narcissism.”
It’s what happens when you feel like people just “aren’t quite on your level.”
“High vibrations,” right?
As the psychiatrist Gerald May wrote in his 1983 book Will and Spirit:
“Simply stated, spiritual narcissism is the unconscious use of spiritual practice, experience, and insight to increase rather than decrease self-importance.”
Spiritual arrogance emerges naturally as we engage on the spiritual path. We fool ourselves into thinking that by taking steps to become more “enlightened,” we’re in some way superior to those who do not.
We leverage spiritual practices — like yoga, meditation, or other forms of spiritual self-care — as tokens of our supposed enlightenment or moral superiority.
We may use our "spiritual" identity to look down upon others who don't share these practices or beliefs, to dodge personal responsibilities or interpersonal challenges, or to create a persona that earns us social capital.
This condition damages both the individual, who is missing the opportunity for genuine spiritual or personal growth, and the community around them, which may be subjected to their judgment, manipulation, or neglect.
The presentation of spiritual arrogance comes in all shapes and sizes.
Let’s say you join a church group or other spiritual group. Members become spiritually proud. They believe they are the ones who have the right teaching. Everybody else is a bit off the track.
Then someone comes and one-ups them. “In our circles, we’re very tolerant. And we accept all teachings and all ways as leading to the one.”
But they’re just playing the game of “we’re more tolerant than you are.”
In essence, they become a victim of their own spiritual practice — they’re blind to the paradox of the spiritual path and become lost in their own egotistical beliefs that their “way” is somehow better than everybody else’s.
Of course, the other side of this paradox comes from noticing the people around you who demonstrate signs of spiritual arrogance. Looking at someone in their arrogance can make you feel like they’re inferior.
It’s another trap — but it comes from the completely opposite angle.
We cannot escape it.
Can Spiritual Arrogance Be Avoided?
Probably not, but by learning to recognize it, we may be able to re-align ourselves towards the middle path when it inevitably appears over and over again throughout our lives.
Here are some ideas to think about for avoiding the paradoxical nature of spiritual arrogance:
1. Find your intuitive expertise & learn to flow with it
Taoists call this practice “wu-wei.” Zen Buddhists call it “mushin.” Both loosely refer to an absence of striving. It’s the constant striving to improve or reach “higher vibrations” that causes this paradox to manifest in a big way.
2. Stop judging others based on their “level”
Spirituality is not a competition; you are not here to “help” others on their spiritual journey.
3. Remain skeptical about ideas, mentors, & gurus
Nobody truly has it figured out, and if they do, they certainly aren’t talking about it.
4. Embrace the beginner’s mind
Avoid bringing your preconceptions and opinions to new ideas. Act as though you’re a child experiencing everything for the first time.
5. Be conscious about your use of social media
This is especially important when it comes to sharing your spiritual development publicly. By sharing with others, you’re feeding the ego hiding behind the curtain.
6. Avoid over-intellectualizing spirituality
This comes at the expense of direct, personal, or experiential understandings of these concepts in daily life.
7. Beware of toxic positivity
This is the belief that no matter how dire or difficult a situation is, people should maintain a positive mindset. This invalidates an authentic human emotional experience and is a form of spiritual bypassing.
Quotes on Spiritual Arrogance
“The biggest ego trip going is getting rid of your ego.” — Alan Watts
“If it’s so easy to lose Jim Carey, who’s Jim Carey?” — Jim Carey
“If an organ is working properly, you don’t feel it. When you’re thinking clearly, your brain isn’t getting in your way.” — Alan Watts
“To go beyond is as wrong as to fall short.” — Confucius
“For things to reveal themselves to us, we need to be ready to abandon our views about them.” — Thich Nhat Hanh
“No matter what the practice or teaching, ego loves to wait in ambush to appropriate spirituality for its own survival and gain.” ― Chögyam Trungpa
Zen Koans About Spiritual Arrogance
The beauty of Zen koans is that they can be used to “impart wisdom” that can’t otherwise be explained by words.
They’re told as a sort of joke — only the punchline isn’t spontaneous laughter — but spontaneous glimpses of enlightenment.
They all deliver some form of unexplainable wisdom that you either get at the punchline or you don’t. Just like a joke, if the koan has to be explained, it loses its power.
Subscribe to The Zen Psychedelic
Thanks for reading The Zen Psychedelic! Consider subscribing for free to receive new posts and support my work.
You can subscribe here using Nostr or follow me on Substack.
→ This post was originally published on The Zen Psychedelic Substack
-
 @ 83279ad2:bd49240d
2025-04-20 08:39:12
@ 83279ad2:bd49240d
2025-04-20 08:39:12Hello
-
 @ c3f12a9a:06c21301
2025-04-19 10:09:45
@ c3f12a9a:06c21301
2025-04-19 10:09:45Satoshi’s Time-Traveling for Knowledge #4: Liberland 2024 – Freedom Under Siege
What is Liberland?
While digging through old decentralized forums archived on the Interchain, Satoshi came across a curious name: Liberland.
“A sovereign libertarian micronation on the Danube? Founded in 2015 via Terra nullius? Built on the principles of freedom, voluntaryism, and Bitcoin? And I’ve never heard of it?”
Intrigued, Satoshi began to research. The story was almost too good to be true. A 7-square-kilometer patch of unclaimed land between Croatia and Serbia, turned into a symbol of decentralized governance and individual liberty.
No taxes unless voluntary. Bitcoin as the national currency. A digital nation-state with thousands of registered e-citizens, and even its own constitution. And yet—no recognition, no borders, and no peace.His curiosity turned into determination. He calibrated the temporal coordinates on his chrono-node to the Danube River in 2024, a year rumored to be turbulent for the Free Republic of Liberland.
When he arrived, reality struck harder than the legend.
Freedom Under Siege
The nation was under siege.
The scent of burnt wood and trampled earth lingered in the air as Satoshi stepped into what remained of the Liberland settlement. Broken structures, crushed solar panels, and a few scattered personal belongings were all that testified to the once-vibrant hub of liberty pioneers.
He found a group of residents—mud-streaked, exhausted, but defiant—gathered around the remnants of a communal kitchen. One of them, wearing a weathered Liberland t-shirt and a crypto-wallet hardware device on a chain around his neck, greeted him:
"You're not with them, are you?"
Satoshi shook his head.
"Just... passing through. What happened here?"
The man’s voice trembled between rage and sorrow:
"On the International Day of Peace, no less. Croatian police raided us. Bulldozers came with them. Took everything—generators, comms gear, even our medical tents. Claimed it was 'illegal occupation of Croatian forestry land.' But no court, no hearing. Just force."
Satoshi listened, taking mental snapshots of their faces, their words, their pain. He thought about the dream—of a place built voluntarily, where people governed themselves, free from coercion.
But that dream was burning at the edges, like the collapsed tents scattered behind them.
Reflections Under the Stars
As night fell over the Danube, Satoshi sat alone, watching the stars reflect on the black water. Thoughts spiraled:
"Decentralization... is beautiful. But without protection, it's fragile."
He realized that so long as central authorities hold monopoly on violence and taxation, every independent effort to decentralize the world—from Bitcoin to Liberland—is at risk of being suppressed, ignored, or destroyed. Not because it’s wrong, but because it's inconvenient to power.
"Unless a major state like the USA decentralizes itself from within," he thought, "true decentralization will remain a resistance—never the standard."
He activated his chrono-node once more. Not in defeat, but with purpose.
The next destination? Unknown. But the mission was clearer than ever.
originally posted at https://stacker.news/items/947954
-
 @ f1f59549:f4121cfe
2025-04-28 20:20:58
@ f1f59549:f4121cfe
2025-04-28 20:20:58Sariputra, one of the Buddha’s chief disciples, was once asked — “What is nirvana?”
He answered — “The destruction of greed, the destruction of anger, the destruction of delusion — this is nirvana.”
The Wheel of Life
The Wheel of Life (Bhavachakra) is a symbolic representation of samsara — the cycle of birth, death, and rebirth. It illustrates the Buddhist understanding of the nature of existence and outlines the path to liberation or nirvana.
 At the center of the wheel, you’ll find depictions of a rooster, a snake, and a pig. These animals represent the 3 poisons, which are the root of suffering and the forces that keep us trapped in the cycle of samsara.
At the center of the wheel, you’ll find depictions of a rooster, a snake, and a pig. These animals represent the 3 poisons, which are the root of suffering and the forces that keep us trapped in the cycle of samsara.These 3 unliberated beings perpetually circle the wheel of life, experiencing birth, death, and rebirth endlessly:
-
The rooster represents greed or overindulgence.
-
The snake represents hatred or anger.
-
The pig represents delusion or ignorance.
 The second layer of the wheel represents karma, which is separated into two halves. The white half depicts beings moving upward towards more fortunate rebirths. The black half depicts beings moving downwards towards less fortunate births.
The second layer of the wheel represents karma, which is separated into two halves. The white half depicts beings moving upward towards more fortunate rebirths. The black half depicts beings moving downwards towards less fortunate births.The third layer depicts the 6 realms of existence — the god realm, the demi-god realm, the human realm, the animal realm, the hungry ghost realm, and the hell realm.
The fourth layer (outer rim) depicts the 12 links of the causal chain that leads to rebirth and suffering — ignorance, formations, consciousness, name and form, six sense bases, contact, feeling, craving, clinging, becoming, birth, and death.
The entire wheel is encompassed by Yama, the Lord of Death. This symbolizes the inevitability of death and the impermanence of all things. The Buddha can be seen beyond the wheel, pointing at the moon. This represents the possibility of liberation from the cycle of samsara.
 # 1. Delusion & Ignorance
# 1. Delusion & IgnoranceDelusion and ignorance are misunderstandings of the true nature of reality that manifest through our ego-driven desires, aversions, and misconceptions.
The ego serves as a reducing valve to make sense of the chaos of existence. It separates I from other and filters the vast information we receive in each waking moment so our brains can comprehend and navigate the complexity of the world around us.
The problem is that in doing so, we jump to conclusions and invent information to satisfy the narratives our ego constructs. All of our opinions and beliefs are baked in delusion — based on information that isn’t complete, is one-sided, or distorted.
Delusion prevents us from seeing the truth. It fuels disagreements, conflict, and misunderstanding. It leads to greed by making us think we need more in order to feel happy, safe, and fulfilled in life. It leads to anger by fostering resentment and hostility towards others and creates barriers that prevent us from seeing their perspectives.
Overcoming these delusions involves engaging in practices that cultivate direct experiential insight, mindfulness, and humility. Developing the willingness to accept and acknowledge our delusions helps us perceive the world as it truly is.
The paradox herein lies in the fact that we cannot be without ego — and that seeking to dismantle it to escape the trap of delusion and ignorance is, in itself, an ignorant goal. The middle way says that we may attempt to escape our delusion and ignorance — but will ultimately fail. In recognizing this, we may find a path to true understanding and enlightenment.
 # 2. Greed & Overindulgence
# 2. Greed & OverindulgenceGreed is the desire for “just a little bit more.” It’s a feeling of being unsatisfied with what we have. This could be money, possessions, power, or status.
There’s always something more we could have.
Photographers want new, better cameras and lenses; musicians want more sophisticated instruments; and tech enthusiasts want the latest gadgets and software.
These small desires for more may not seem like “poison” per se — but while innocuous on the surface, they signal a greater underlying dissatisfaction.
On the extreme end of greed is addiction — living perpetually from one fix to the next. Whether it’s drugs, sex, gambling, shopping, or food — the addict is obsessed with obtaining more to the point where it becomes an undeniable detriment to their health, their relationships, and their ability to feel happy.
Zen Buddhism posits that the antidote to greed is detachment. By striving for minimalism in all areas of our life — learning to make do with less and be content with what we have — we may undermine the insidious power of greed and overindulgence.
 # 3. Hatred & Anger
# 3. Hatred & AngerHatred and anger arise from fear and delusion. When we encounter something or someone that threatens or exposes the beliefs, desires, or vulnerabilities of the ego, our natural response is to defend it through hostility. This hostility is an unconscious reaction that further clouds our judgment, reinforces our delusions, and prevents us from seeing the true nature of things.
Zen Buddhism teaches that the antidote to hatred is compassion. By cultivating a sense of empathy towards others and seeking to understand their perspective, we can break the barriers that fuel our anger and cloud our judgment. This is taught through mindfulness practices that help us identify and acknowledge the emotion of anger and allow us to choose how we respond rather than reacting unconsciously.
Our emotions are transient and non-defining — we are allowed to feel anger, but applying it through hostility and cementing it in hatred only leads to further delusion and suffering.
Opposing the 3 Poisons
Buddhism teaches that the antidotes against the 3 poisons and fundamental steps toward liberation are wisdom/insight, generosity/detachment, and lovingkindness/compassion.
Wisdom and insight are the direct antidotes to delusion and ignorance. Practices like meditation, dedicated study, and reflective contemplation help us cultivate a deeper understanding of the true nature of reality and break through the misconceptions that bind us to suffering.
Detachment and generosity counter greed and attachment by encouraging a spirit of giving and letting go. It shifts our focus from accumulating more to sharing what we have.
Lovingkindness and compassion are cultivated to dissolve anger and hatred. Through practices like Metta meditation and active empathy, we may learn to extend feelings of unconditional love and understanding toward ourselves and others. This practice helps us overcome the defensive and hostile reactions that arise from threatened egos and fosters a more inclusive and peaceful interaction with the world.
While we cannot be entirely rid of these poisons, we can learn to identify how they manifest in our lives and develop techniques that mitigate their influence over our thoughts and actions.
Subscribe to The Zen Psychedelic
Thanks for reading The Zen Psychedelic! Consider subscribing for free to receive new posts and support my work.
You can subscribe here using Nostr or follow me on Substack.
→ This post was originally published on The Zen Psychedelic Substack
-
-
 @ c4b5369a:b812dbd6
2025-04-15 07:26:16
@ c4b5369a:b812dbd6
2025-04-15 07:26:16Offline transactions with Cashu
Over the past few weeks, I've been busy implementing offline capabilities into nutstash. I think this is one of the key value propositions of ecash, beinga a bearer instrument that can be used without internet access.
 It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!
It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!What is ecash/Cashu?
Ecash is the first cryptocurrency ever invented. It was created by David Chaum in 1983. It uses a blind signature scheme, which allows users to prove ownership of a token without revealing a link to its origin. These tokens are what we call ecash. They are bearer instruments, meaning that anyone who possesses a copy of them, is considered the owner.
Cashu is an implementation of ecash, built to tightly interact with Bitcoin, more specifically the Bitcoin lightning network. In the Cashu ecosystem,
Mintsare the gateway to the lightning network. They provide the infrastructure to access the lightning network, pay invoices and receive payments. Instead of relying on a traditional ledger scheme like other custodians do, the mint issues ecash tokens, to represent the value held by the users.How do normal Cashu transactions work?
A Cashu transaction happens when the sender gives a copy of his ecash token to the receiver. This can happen by any means imaginable. You could send the token through email, messenger, or even by pidgeon. One of the common ways to transfer ecash is via QR code.
The transaction is however not finalized just yet! In order to make sure the sender cannot double-spend their copy of the token, the receiver must do what we call a
swap. A swap is essentially exchanging an ecash token for a new one at the mint, invalidating the old token in the process. This ensures that the sender can no longer use the same token to spend elsewhere, and the value has been transferred to the receiver.
What about offline transactions?
Sending offline
Sending offline is very simple. The ecash tokens are stored on your device. Thus, no internet connection is required to access them. You can litteraly just take them, and give them to someone. The most convenient way is usually through a local transmission protocol, like NFC, QR code, Bluetooth, etc.
The one thing to consider when sending offline is that ecash tokens come in form of "coins" or "notes". The technical term we use in Cashu is
Proof. It "proofs" to the mint that you own a certain amount of value. Since these proofs have a fixed value attached to them, much like UTXOs in Bitcoin do, you would need proofs with a value that matches what you want to send. You can mix and match multiple proofs together to create a token that matches the amount you want to send. But, if you don't have proofs that match the amount, you would need to go online and swap for the needed proofs at the mint.Another limitation is, that you cannot create custom proofs offline. For example, if you would want to lock the ecash to a certain pubkey, or add a timelock to the proof, you would need to go online and create a new custom proof at the mint.
Receiving offline
You might think: well, if I trust the sender, I don't need to be swapping the token right away!
You're absolutely correct. If you trust the sender, you can simply accept their ecash token without needing to swap it immediately.
This is already really useful, since it gives you a way to receive a payment from a friend or close aquaintance without having to worry about connectivity. It's almost just like physical cash!
It does however not work if the sender is untrusted. We have to use a different scheme to be able to receive payments from someone we don't trust.
Receiving offline from an untrusted sender
To be able to receive payments from an untrusted sender, we need the sender to create a custom proof for us. As we've seen before, this requires the sender to go online.
The sender needs to create a token that has the following properties, so that the receciver can verify it offline:
- It must be locked to ONLY the receiver's public key
- It must include an
offline signature proof(DLEQ proof) - If it contains a timelock & refund clause, it must be set to a time in the future that is acceptable for the receiver
- It cannot contain duplicate proofs (double-spend)
- It cannot contain proofs that the receiver has already received before (double-spend)

If all of these conditions are met, then the receiver can verify the proof offline and accept the payment. This allows us to receive payments from anyone, even if we don't trust them.
At first glance, this scheme seems kinda useless. It requires the sender to go online, which defeats the purpose of having an offline payment system.
I beleive there are a couple of ways this scheme might be useful nonetheless:
-
Offline vending machines: Imagine you have an offline vending machine that accepts payments from anyone. The vending machine could use this scheme to verify payments without needing to go online itself. We can assume that the sender is able to go online and create a valid token, but the receiver doesn't need to be online to verify it.
-
Offline marketplaces: Imagine you have an offline marketplace where buyers and sellers can trade goods and services. Before going to the marketplace the sender already knows where he will be spending the money. The sender could create a valid token before going to the marketplace, using the merchants public key as a lock, and adding a refund clause to redeem any unspent ecash after it expires. In this case, neither the sender nor the receiver needs to go online to complete the transaction.
How to use this
Pretty much all cashu wallets allow you to send tokens offline. This is because all that the wallet needs to do is to look if it can create the desired amount from the proofs stored locally. If yes, it will automatically create the token offline.
Receiving offline tokens is currently only supported by nutstash (experimental).
To create an offline receivable token, the sender needs to lock it to the receiver's public key. Currently there is no refund clause! So be careful that you don't get accidentally locked out of your funds!

The receiver can then inspect the token and decide if it is safe to accept without a swap. If all checks are green, they can accept the token offline without trusting the sender.

The receiver will see the unswapped tokens on the wallet homescreen. They will need to manually swap them later when they are online again.
 Later when the receiver is online again, they can swap the token for a fresh one.
Later when the receiver is online again, they can swap the token for a fresh one.
Summary
We learned that offline transactions are possible with ecash, but there are some limitations. It either requires trusting the sender, or relying on either the sender or receiver to be online to verify the tokens, or create tokens that can be verified offline by the receiver.
I hope this short article was helpful in understanding how ecash works and its potential for offline transactions.
Cheers,
Gandlaf
-
 @ 57d1a264:69f1fee1
2025-04-29 05:43:02
@ 57d1a264:69f1fee1
2025-04-29 05:43:02A debonair day-to-night hideaway fuses heritage charm with contemporary flair in the Penang capital of George Town...
Housed in a historic landmark on George Town’s atmospheric Lebuh Farquhar, just a stone’s throw from the iconic Eastern & Oriental Hotel, MOJO JOJO is a café and brunch spot by day, and a refined eatery come nightfall. With an effortlessly cool edge, the space has been designed by Empt Studio and combines contemporary charm with the energy of this Malaysian city.
Split into two sections, the venue caters to both hotel guests and passersby. One side offers an intimate, tailored dining experience for those seeking a respite from the buzz of outside, while the other spills out onto the street, embracing George Town’s lively buzz. The soaring ceilings create a sense of openness, further enhanced by the introduction of a mezzanine above the kitchen, maximising space without compromising on airiness.
Natural materials feature throughout with custom bamboo display systems and solid Nyatoh timber fixtures lending a rich, textural warmth. Deliberately crafted interlocking joints pay homage to traditional woodworking techniques, reinforcing both strength and authenticity. Every detail nods to meticulous craftsmanship, from the aged wood grains to the earthy material palette that echoes the heritage of its surroundings.
Lighting plays a supporting yet pivotal role, with carefully curated, softly diffused illumination accentuating the textures and forms within. The interplay of warm light and natural materials fosters an immersive, atmospheric retreat from the fast-paced city outside.
A refuge for slow mornings and, later on, offering a more cultured affair, MOJO JOJO is a debonair dining spot for the handsome Penang capital.
Read more https://www.emptstudio.com/projects/mojojojo
originally posted at https://stacker.news/items/966008
-
 @ f1f59549:f4121cfe
2025-04-28 20:20:18
@ f1f59549:f4121cfe
2025-04-28 20:20:18Zen Buddhism teaches simplicity, naturalness, and direct experiential wisdom (called Kenshō) as a means to attain enlightenment. This sort of wisdom is typically earned through long hours of sitting meditation (called zazen) — which eventually exhausts the ego and its constant chatter.
The idea is that through meditation, one can achieve complete awareness. During this state, one holds no expectations, no attachment, and no judgment. Zen practitioners can make observations about the self and the world around them without projecting internal biases or opinions.
Through this profound clarity, insights about life, death, and the nature of reality present themselves in ways impossible to describe. These insights cannot be taught or intellectualized; they can only be experienced firsthand.
Certain psychedelics, such as LSD, DMT, or psilocybin, may offer a shortcut — sort of. These substances have the remarkable ability to provide glimpses of this ineffable wisdom.
Psychedelics produce on-demand exposure to so-called "direct experience." They inject users into states similar to the ones hose cultivated by Zen Buddhists and many other spiritual traditions over many months or years.
With that said, psychedelics may not be quite the shortcut we'd hope they could be, and there are some significant caveats to using them. Their effects vary widely from one session to another, often leading to experiences that are more confusing than enlightening. Even in times when they are profoundly insightful, the insight gained dissipates quickly if not properly integrated and supported by consistent practice or guidance.
The Mystical Experience
One of the great virtues of magic mushrooms and other classical psychedelics is their capacity to induce powerful — often life-changing, religious experiences. Psychologists call this the "mystical experience."
Some examples of phenomena reported by patients who fit the criteria for having had psychedelic-induced mystical experiences include seeing the interconnectedness of all things, separation from ego, realization that all things are a manifestation of the same universal energy, and meetings with divine entities.
These states are powerful. A study from Johns' Hopkins in 2006 reported that 67% of study participants who were given psilocybin claimed the experience to be the single most meaningful experience of their life.
Profound as the psychedelic experience may be, the insight they provide is only temporary. If you don't return to life, you won't bring enlightenment back with you — you're merely visiting the place where enlightenment exists.
As an old Zen proverb puts it:
"Before enlightenment, chop wood, carry water. After enlightenment, chop wood, carry water."
Psychologist and renowned American Theravada Buddhist teacher Jack Kornfield says:
"Yes, awakening comes in a moment, but living it, stabilizing it can take months, years, and lifetimes."
I like to think of the psychedelic-induced mystical experience as a sort of "free trial" of what enlightenment might feel like — but it only becomes a reality if you can integrate it into your daily life… a process that requires dedication and effort.
Psychedelics & the Illusion of Clarity
Speaking on the topic of psychedelics and spiritual insight, legendary psychologist Carl Jung once cautioned us to "beware of unearned wisdom."
The implication is that although psychedelics can provide us with on-demand revelations about the nature of the self and the universe — without a solid framework to truly understand and integrate these experiences, we paradoxically run the risk of causing further delusion and inflation of ego.
Overuse of psychedelics or experimentation with psychedelics without first establishing a solid philosophical/spiritual foundation could paradoxically strengthen the ego and one's attachments to the drug itself and the experiences it creates.
Most people who have used psychedelics have experienced those "aha!" moments. In these moments, everything suddenly makes sense.
But these insights are fleeting — like a clump of sand slipping through your fingers. One minute, it's there, vivid and clear; the next, only a few grains of sand remain clinging to your hands.
Even if you remember parts of the experience, without properly integrating these ideas into one's daily life, they become buried by the passage of time.
I've had several of these "aha!" moments from psychedelics. Some were strong enough to completely alter the direction of my life. But after just a few short weeks, these insights and their impact were nowhere to be found.
This is where the benefit of a disciplined spiritual practice comes in.
The Slow, Disciplined Approach
Structured spiritual practices, such as Zen Buddhism, Hinduism, and Taoism, all emphasize the cultivation of steady routines around one's spiritual development. This may include long hours of daily meditation, constant reaffirmation of simplicity, deep personal reflection, and a disciplined approach to one's daily responsibilities.
These practices allow space for us to constantly reassess what we think we know about ourselves and about the nature of reality and to address topics we unconsciously try to avoid or disregard — like death, impermanence, and the illusion imposed by the ego.
Structured spiritual practice, regardless of its form, gives us the opportunity to more thoroughly integrate the insights gained through psychedelics so they remain and compound long-term. They also offer a framework in which to attain similar cosmic knowledge without relying on altering our pharmacology.
These practices are much more sustainable long-term and allow the insights gained from psychedelics to compound and grow over time rather than fostering further delusion and ego.
 # Using Psychedelics "Mindfully"
# Using Psychedelics "Mindfully"Psychedelics can act as a gateway to cosmic insight — but they're merely one of many tools we can pull from as part of our broader spiritual toolbox. The trick is to use the right tool for the job.
You wouldn't use a hammer to drive a screw, and a crowbar is overkill for opening a can of paint.
In the same way, psychedelics shouldn't be the sole method of seeking spiritual enlightenment but rather a complement to grounded practices and structured learning. Just as a tool can cause damage when misused, the unmoderated or thoughtless use of psychedelics can lead to misunderstandings or further cloud one's path.
Use them, learn to "let go," and allow the insights received to leave their mark and then dissipate. Avoid clinging to these insights.
As Dudjom Rinpoche puts it:
"If you see anything horrible, don't cling to it; if you see anything beautiful, don't cling to it."
That said, many people do find value in the insights gained from responsible, respectful use of psychedelics, particularly when those experiences are approached with the kind of mindful, non-attached awareness that is cultivated in Zen practice.
I'll conclude by suggesting that the supplementation of insights gained through the use of psychedelics, with a consistent practice like Zen meditation, can help us understand, integrate, and truly "earn" the wisdom these visionary substances have to offer.
Are "Shortcuts" Allowed in Traditional Spiritual Practice?
There's a lot of debate about the position of psychedelics in traditional spiritual practice. In Buddhism, the Fifth Precept advises against the consumption of intoxicants. The wording of the Fifth Precept varies somewhat depending on the translation, but is commonly rendered in English as something along the lines of:
"I refrain from taking intoxicants which lead to heedlessness."
Some take this to suggest that the use of any mind-altering substance is bad. They believe maintaining clarity of mind is essential to realizing greater "truths" about the nature of reality.
However, many Zen teachers, including Shunryu Suzuki Roshi, have clarified that this precept is more specific to the "unmindful" use of intoxicants. The idea of a "shortcut" through psychedelics doesn't run antithetical to the teachings of Zen Buddhism.
"People who have started to come to the zendo from LSD experiences have shown an ability to get into good zazen (sitting meditation) very rapidly" — Shunryu Suzuki Roshi.
When the Dalai Lama was asked if students could use drugs to attain enlightenment, he said, "I sure hope so."
Zen is centered around the idea that the nature of mind and consciousness is non-dualistic. This means there is no such thing as a "shortcut" because there is no path to be followed in the first place. There is no right or wrong way to do anything.
Zen teachings say that enlightenment is everpresent — all the meditation, simplification of thought and material, and ritual involved with Zen Buddhism are simply tools to help dissolve the ego and uncover this inherent clarity.
Psychedelic plants, fungi, and even synthetic molecules are just another set of tools we have at our disposal to explore the depths of consciousness as we slowly but surely uncover this elusive but ever-present enlightenment.
Subscribe to The Zen Psychedelic
Thanks for reading The Zen Psychedelic! Consider subscribing for free to receive new posts and support my work.
You can subscribe here using Nostr or follow me on Substack.
→ This post was originally published on The Zen Psychedelic Substack
-
 @ 57d1a264:69f1fee1
2025-04-29 05:23:45
@ 57d1a264:69f1fee1
2025-04-29 05:23:45Hubless Wheels + Donut Motor brings manufacturing & performance benefits
Verge Next, a subsidiary of Estonia-based Verge Motorcycles, invented this Donut Motor. It's designed to drive a hubless wheel. Although once seen as something that simply looked cool in renderings, the company says the hubless arrangement brings performance and manufacturing benefits, "delivering unmatched torque and power density with minimal weight."
For one thing, there's no chain, belt or drivetrain required. Secondly, it frees the body of the bike from the task of holding the motor—everything is now contained within that rear wheel.
The company has not only incorporated the Donut Motor into their own bikes, but is now licensing the technology. Assuming it does what it says on the tin, our future streetscapes will be covered with hubless bikes, scooters and motorcycles.
Here's a closer look at a Verge bike and how its design is influenced by the motor:
https://www.youtube.com/watch?v=Og9vlJRe2-M
originally posted at https://stacker.news/items/966001
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ c1e9ab3a:9cb56b43
2025-04-14 21:20:08
@ c1e9ab3a:9cb56b43
2025-04-14 21:20:08In an age where culture often precedes policy, a subtle yet potent mechanism may be at play in the shaping of American perspectives on gun ownership. Rather than directly challenging the Second Amendment through legislation alone, a more insidious strategy may involve reshaping the cultural and social norms surrounding firearms—by conditioning the population, starting at its most impressionable point: the public school system.
The Cultural Lever of Language
Unlike Orwell's 1984, where language is controlled by removing words from the lexicon, this modern approach may hinge instead on instilling fear around specific words or topics—guns, firearms, and self-defense among them. The goal is not to erase the language but to embed a taboo so deep that people voluntarily avoid these terms out of social self-preservation. Children, teachers, and parents begin to internalize a fear of even mentioning weapons, not because the words are illegal, but because the cultural consequences are severe.
The Role of Teachers in Social Programming
Teachers, particularly in primary and middle schools, serve not only as educational authorities but also as social regulators. The frequent argument against homeschooling—that children will not be "properly socialized"—reveals an implicit understanding that schools play a critical role in setting behavioral norms. Children learn what is acceptable not just academically but socially. Rules, discipline, and behavioral expectations are laid down by teachers, often reinforced through peer pressure and institutional authority.
This places teachers in a unique position of influence. If fear is instilled in these educators—fear that one of their students could become the next school shooter—their response is likely to lean toward overcorrection. That overcorrection may manifest as a total intolerance for any conversation about weapons, regardless of the context. Innocent remarks or imaginative stories from young children are interpreted as red flags, triggering intervention from administrators and warnings to parents.
Fear as a Policy Catalyst
School shootings, such as the one at Columbine, serve as the fulcrum for this fear-based conditioning. Each highly publicized tragedy becomes a national spectacle, not only for mourning but also for cementing the idea that any child could become a threat. Media cycles perpetuate this narrative with relentless coverage and emotional appeals, ensuring that each incident becomes embedded in the public consciousness.
The side effect of this focus is the generation of copycat behavior, which, in turn, justifies further media attention and tighter controls. Schools install security systems, metal detectors, and armed guards—not simply to stop violence, but to serve as a daily reminder to children and staff alike: guns are dangerous, ubiquitous, and potentially present at any moment. This daily ritual reinforces the idea that the very discussion of firearms is a precursor to violence.
Policy and Practice: The Zero-Tolerance Feedback Loop
Federal and district-level policies begin to reflect this cultural shift. A child mentioning a gun in class—even in a non-threatening or imaginative context—is flagged for intervention. Zero-tolerance rules leave no room for context or intent. Teachers and administrators, fearing for their careers or safety, comply eagerly with these guidelines, interpreting them as moral obligations rather than bureaucratic policies.
The result is a generation of students conditioned to associate firearms with social ostracism, disciplinary action, and latent danger. The Second Amendment, once seen as a cultural cornerstone of American liberty and self-reliance, is transformed into an artifact of suspicion and anxiety.
Long-Term Consequences: A Nation Re-Socialized
Over time, this fear-based reshaping of discourse creates adults who not only avoid discussing guns but view them as morally reprehensible. Their aversion is not grounded in legal logic or political philosophy, but in deeply embedded emotional programming begun in early childhood. The cultural weight against firearms becomes so great that even those inclined to support gun rights feel the need to self-censor.
As fewer people grow up discussing, learning about, or responsibly handling firearms, the social understanding of the Second Amendment erodes. Without cultural reinforcement, its value becomes abstract and its defenders marginalized. In this way, the right to bear arms is not abolished by law—it is dismantled by language, fear, and the subtle recalibration of social norms.
Conclusion
This theoretical strategy does not require a single change to the Constitution. It relies instead on the long game of cultural transformation, beginning with the youngest minds and reinforced by fear-driven policy and media narratives. The outcome is a society that views the Second Amendment not as a safeguard of liberty, but as an anachronism too dangerous to mention.
By controlling the language through social consequences and fear, a nation can be taught not just to disarm, but to believe it chose to do so freely. That, perhaps, is the most powerful form of control of all.
-
 @ 5f078e90:b2bacaa3
2025-04-28 19:44:00
@ 5f078e90:b2bacaa3
2025-04-28 19:44:00This is a test written in yakihonne.com as a long form article. It is a kind 30023. It should be cross-posted to Hive.













