-
 @ 2b24a1fa:17750f64
2025-05-02 13:40:12
@ 2b24a1fa:17750f64
2025-05-02 13:40:12Das Kriegsgrauen kriecht unter die Haut. Bilder von verstümmelten Beinen und Armen, von Kriegstraumatisierten schweigenden Männern, von Kriegsgräbern steigen auf. Als Mutter, Schwester, Tante, Großmutter wachsen die Ängste, dass sich ein Verwandter von der politischen und medialen Kriegslust anstecken lässt und tatsächlich die Beteiligung an den näher kommenden kriegerischen Auseinandersetzungen in Erwägung zieht. Einen wütenden Kommentar anlässlich der wachsenden Kriegstreiberei verfasste unser Autor Nicolas Riedl.
https://soundcloud.com/radiomuenchen/sofa-soldaten-an-die-front-von-nicolas-riedl?
Bild: KI
-
 @ 99e7936f:d5d2197c
2025-05-02 13:25:06
@ 99e7936f:d5d2197c
2025-05-02 13:25:06Frieden braucht die Kapitulation, keine Gebrauchsanweisung
Wenn Dir ständig jemand erklärt, wie Du etwas zu machen hast, dann machst Du irgendwann gar nichts mehr, sondern wartest nur noch auf die nächste Aufforderung, dies oder jenes zu tun.
Manchmal ist das gut so, aber meist ist diese abwartende Haltung eine Vorlage für andere Menschen, die nichts Gutes im Schilde führen. Sie nutzen dieses entgegengebrachte Vertrauen aus und geben Anweisungen, die nur ihnen selbst dienen und sonst keinem. Das Phänomen ist hinreichend bekannt.
Ich habe lange gebraucht, um zu verstehen, warum Menschen auf Aufforderungen von anderen warten. Das ist offensichtlich früh gelerntes Verhalten, wie so vieles im Leben. In meiner Kindheit habe ich auch viele dysfunktionale Verhaltensweisen gelernt, aber exakt diese nicht, da ich kaum Aufforderungen erhielt. Ich hätte gerne welche erhalten. Meine Eltern waren aber meist mit sich selbst und den Anforderungen des Alltags beschäftigt.
Mein Vater war 11 Jahre und meine Mutter war 8 Jahre alt als der zweite Weltkrieg endete. Zwanzig Jahre später kreuzten sich ihre Wege, sie heirateten und bekamen drei Kinder. Sie kümmerten sich um alle praktischen Aufgaben, sorgten für Sicherheit, ein schönes Zuhause und materiellen Wohlstand. Ich muss schlucken beim Schreiben dieses Satzes.
Mit 11 Jahren fing ich an, Tagebuch zu schreiben, weil ich so vieles nicht verstand. Trauma wird weiter gegeben, wenn es nicht aufgelöst wird. Ich hätte, wie gesagt, gerne mal klare Aufforderungen und Anweisungen gehabt. Ich suchte in der Schule und in meinen Ausbildungen nach Antworten, fand sie aber nicht. 1990 war ich 20 Jahre alt und startete nicht gut vorbereitet ins Erwachsenenleben. Wenn ich heute auf die letzten 35 Jahre zurück blicke, dann verstehe ich so viel, dass mir schwindelig wird. Heute mag ich mich und bereite mich daher nur noch selten auf etwas vor. Diese Erkenntnis ist aber nicht über Nacht gekommen. Das hätte ich wohl kaum überlebt. Die hierzu notwendigen Krisen in meinem Leben kamen in regelmäßigen Abständen und waren wohldosiert. Mit Krisen kenne ich mich aus. Krisen folgen immer demselben Muster, egal ob persönliche oder globale.
Wer bin ich, und warum schreibe ich hier einen Artikel über Frieden?
Ich bin eine Psychologin, die sich für ihr Leben gern mit Trauma beschäftigt. Das ist, nebenbei bemerkt, eines der positivsten Themen, die es gibt. Aber dazu erzähle ich ein anderes Mal. Ich bin das Kind meiner Eltern, Spätentwicklerin und die Eiskönigin nach der Verwandlung. Menschen, die meine Geschichte nicht kennen, halten mich für stark, obwohl ich auch nicht stärker bin als andere. Bewältigtes Trauma macht einen stark. Seitdem ich vor ein paar Jahren meinen persönlichen Knoten gelöst habe, folge ich nur noch meinem Herzen, was unglaublich polarisiert. Ich kann jetzt nicht mehr anders. Früher habe ich mein Herz zwar auch schon deutlich gehört, aber überholte Glaubenssätze hatten oft das letzte Wort und bestimmten mein Handeln. Das war dann nicht selten der innerliche Spagat, um es vor allem anderen recht zu machen. Die leere Batterie, die ich mehrmals kennen lernen durfte, hat mich dann gelehrt, es anders zu machen. Heute achte ich auf meine sehr feine Wahrnehmung und auf meine Bedürfnisse. Das kommt aber meistens auch anderen zugute.
Wer gelernt hat, sich selbst so anzunehmen wie er ist, was gleichzusetzen ist mit Schmerz, der möchte anderen keinen Schmerz zufügen. Eigentlich könnte ich an dieser Stelle den Artikel schon beenden.
Selbstliebe und Schmerz sind unzertrennliche Freunde. Aber dazu erzähle ich auch ein anderes Mal.
Heute möchte ich etwas dazu sagen, warum ich für den Frieden keine Gebrauchsanweisung brauche, sondern die Kapitulation.
Ich bin dem Krieg * in* mir begegnet. Dieser Krieg hat in meinem Außen über lange Zeit für Unruhe gesorgt, und er hat meine Batterie im Innern dadurch öfters leer gezogen. Er war immer berechtigt, begründet und gerechtfertigt, aber dennoch nicht gut für mich oder andere. Im größten Schmerz, den ich je empfunden habe, kam dann 2018/19 endlich der Frieden in mein persönliches Leben. Ich musste dafür nichts tun. Ausrufungszeichen. Den Frieden bekam ich quasi geschenkt, weil ich aufgehört hatte zu kämpfen, weil ich mich dem Schmerz hingegeben hatte, weil ich es akzeptiert hatte, am Boden zu liegen.
Alle wollen Frieden, aber niemand will am Boden liegen.
Kann ich gut verstehen, aber meine Erfahrung ist genau diese, dass Du gefühlt am Boden liegen musst. Frieden kann man „machen“ durch bewusstes Unterlassen von verbalem Zurückschlagen und von Ablenkungs- oder Vermeidungsverhalten, um den eigenen Schmerz nicht spüren zu müssen. Nach diesem Verzicht kann man dann Wut und Schmerz deutlicher oder sogar hervorragend spüren, und dann kommt das Geschenk. Der Frieden durchflutet Dich in einem Moment, in dem Du es nicht erwartest. Frieden kommt, wenn die Situation gefährlich und existenziell bedrohlich wird. Der ganze Körper entspannt in einem einzigen Moment. Das ist wie eine Erlösung. Man sagt nicht umsonst, dass es schön sei, wenn der Schmerz aufhöre. Das stimmt wirklich. Da passiert auch auf biologischer Ebene ganz viel. Körpereigene Stoffe, die schmerzfrei und unglaublich leicht fühlen lassen, werden in Hülle und Fülle ausgeschüttet. Die Evolution hat an alles gedacht. Sie lässt Dich nicht im Stich, wenn es dicke kommt. Frieden ist ein unbeschreiblicher Zustand. Wenn Du den einmal gespürt hast, dann ist der Weg frei, und dann brauchst Du keine Gebrauchsanweisung mehr. Dieser Moment verändert Dich für immer. Du hast eine Erfahrung gemacht, die Dir keiner mehr nehmen kann. Ich habe diese Erfahrung damals alleine gemacht, weil ich niemanden hatte, dem ich mich anvertrauen wollte. Das war ganz unspektakulär im Wohnzimmer. Aber diese Erfahrung, für die es tausende von Bezeichnungen gibt, verändert Dein Leben von Grund auf. Schön ist, wenn man jemanden an seiner Seite hat, der einfach nur zuhört und ab und zu einfach mal was Nettes sagt. Und genau das ist so schwer, so jemanden zu finden, der gerne bei einem sein möchte, wenn man gerade gefühlt stirbt. Die meisten Menschen laufen dann weg oder sagen: „Jetzt reiß Dich mal zusammen.“
Frieden ist nichts für schwache Nerven.
Wenn Du Frieden einmal selbst am eigenen Körper erlebt hast, dann gehst Du anders in Auseinandersetzungen (und globale Krisen) hinein, weil Du diesen Mechanismus kennen gelernt hast, weil Du weißt, dass Du geschützt bist. Das Leben liebt Dich und arbeitet für Dich. Immer. Mit diesem Wissen ausgestattet, kannst Du leichter ruhig bleiben, wenn es nicht so gut läuft, wenn es brenzlig wird, auch wenn große Dinge in der Welt schief laufen. Der Schmerz ist nicht mehr Dein Feind, den es unbedingt zu vermeiden gilt. Jetzt wird es kurios. Ich mag sicherlich keinen Schmerz, aber ich laufe vor „dem Schmerz“ nicht mehr davon. Oft empfinden wir Schmerz schon, wenn jemand unsere Glaubenssätze triggert. Ich schau mir den Schmerz an, fühle rein und höre zu, was er mir sagen will. Und in den meisten Fällen ist es gar nicht MEIN Schmerz. Jemand greift mich an, weil er selber Ängste hat, sich getriggert fühlt oder sonst etwas hat oder nicht hat. Ich bin irritiert und vielleicht auch wütend, weil es weh tut, aber genau dann kommt dieses erfahrene Wissen zum Einsatz und legt die rettende Pause in mein Denken und Handeln ein. Ich reagiere nicht mit einem Schlagabtausch, und freu mich umgehend unglaublich über mich selbst. Und dann laufen die Dinge für mich. Ich brauche nur Geduld. Der andere hat jetzt etwas zum Nachdenken. Wenn man nicht zurück schlägt, dann hat der andere etwas zum Nachdenken. Das ist jetzt die Kurzfassung der Geschichte. Jedenfalls aktiviert dieses Unterlassen von Schlagabtausch auch in den schwierigsten Zeitgenossen etwas Gutes. Versprochen. Und dieses Gute fängt dann an zu arbeiten, für mich, für uns alle und vor allem für den Frieden.
Das Ganze ist eine komplexe Erfahrung, die ich erst persönlich gemacht habe, dann aber auch bei anderen beobachten und raushören konnte. Über das Phänomen wird viel geredet. Aber zentral wichtig ist mir zu sagen, dass der Frieden kommt, wenn Du aufgibst, nicht mehr kämpfst, auf einen Schlagabtausch verzichtest. Das gilt für Deine Freundschaften, für Deine Partnerschaft, für Deine Familie und für das Land, in dem Du lebst. Frieden entsteht im Streit, im Krieg. Frieden entsteht, wenn die Situation einen unglaublich verletzt, wütend und fassungslos macht. Die Evolution braucht Dich an Deinem persönlichen Siedepunkt, Schmelzpunkt. Nenn es, wie Du willst. Im Schmerz öffnet sich ein Zugang zu einem anderen Bewusstsein. Du wirst weit auf allen Ebenen. Alles, was Du auf Deinem Weg mal verloren hast, kommt zu Dir zurück. Der Schmerz repariert erst Dich und dann alle anderen, mit denen Du zu tun hast. Menschen, die diese Erfahrung am eigenen Körper gemacht haben, schauen anders auf und in diese Welt, weil sie diese andere Welt, dieses weite Bewusstsein, kennen gelernt haben. Es gibt viele Wege zu diesem weiten Bewusstsein und, nebenbei bemerkt, auch viel Zensur zum Thema in der wissenschaftlichen Welt, aber auch im Mainstream. Ich persönlich habe das Phänomen am eigenen Körper kennen gelernt, bevor ich einen Namen dafür hatte. Aber der wichtige Punkt ist, wenn mich jemand fragen würde, was man mitten im Krieg tun kann, dann würde ich sagen: „Lass den Schmerz zu.“
Soll das etwa heißen, dass der ganze Widerstand aktuell für die Katze ist? Nein, natürlich nicht.
Über Missstände berichten? Ja. Schuldige benennen? Ja. Rechtsstaatliche Maßnahmen? Ja.
Aber lass Deinen Schmerz zu. Spür nach, was genau Dich so wütend macht. Frag Dich konkret, warum Dich das Verhalten von XY so trifft. Warum kann Dich jemand, den Du gar nicht persönlich kennst, so fassungslos machen? Und dann kommen wir alle unweigerlich zu uns selbst. Was ist mir so unglaublich wichtig? Und warum? Und was hat das mit meinen Wunden zu tun?
Mich kann man heute auch immer noch triggern, weil ich ein Mensch aus Fleisch und Blut bin. Aber ich setze mich jedes Mal wieder hin und schaue es mir an, was da noch weh tut in mir. Und dann bin ich bei mir. Und dann geht’s um mich. Und dann gebe ich mir alles Gute, Nährende, Pflegende und Aufmunternde. Das tut mir gut und bringt mich weiter. Und mit dieser Haltung kann ich dann wieder auf Menschen zugehen, denen ich nicht aus dem Weg gehen kann. Und Menschen, die dieser Gesellschaft aktiv Schaden zufügen, kann ich nicht aus dem Weg gehen. Sie sägen an meinem Baum. Sie sägen, aber ich stell mich immer wieder daneben. Ich rede mit ihnen wie mit einem normalen Menschen. Ausrufungszeichen. Ich adressiere das im anderen, was ich wachsen sehen möchte. Ich brauche Pausen, aber ich bleibe ruhig, denn nur so arbeitet das Gute im anderen für mich, für uns alle, für den Frieden. Das Gute im anderen ist in 99,9 % der Fälle da und erreichbar, ist zumindest meine Erfahrung.
Die Erfahrung von Frieden kann mir keiner mehr nehmen.
Und eine Gebrauchsanweisung für den Frieden brauche ich auch nicht mehr.
Kapitulation bringt Frieden.
-
 @ 87f5e1d9:e251d8f4
2025-05-02 13:15:23
@ 87f5e1d9:e251d8f4
2025-05-02 13:15:23In the world of cryptocurrency, the stakes are high, and losing access to your digital assets can be a nightmare. But fear not — Crypt Recver is here to turn that nightmare into a dream come true! With expert-led recovery services and cutting-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
Why Choose Crypt Recver? 🤔 🔑 Expertise You Can Trust At Crypt Recver, we combine state-of-the-art technology with skilled engineers who have a proven track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or dealt with damaged hardware wallets, our team is equipped to help.
⚡ Fast Recovery Process Time is of the essence when it comes to recovering lost funds. Crypt Recver’s systems are optimized for speed, enabling quick recoveries — so you can get back to what matters most: trading and investing.
🎯 High Success Rate With over a 90% success rate, our recovery team has helped countless clients regain access to their lost assets. We understand the intricacies of cryptocurrency and are dedicated to providing effective solutions.
🛡️ Confidential & Secure Your privacy is our priority. All recovery sessions at Crypt Recver are encrypted and kept entirely confidential. You can trust us with your information, knowing that we maintain the highest standards of security.
🔧 Advanced Recovery Tools We use proprietary tools and techniques to handle complex recovery scenarios, from recovering corrupted wallets to restoring coins from invalid addresses. No matter how challenging the situation, we have a plan.
Our Recovery Services Include: 📈 Bitcoin Recovery: Have you lost access to your Bitcoin wallet? We can help you recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds! Cold Wallet Restoration: Did your cold wallet fail? We specialize in extracting assets safely and securely. Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security. Don’t Let Lost Crypto Ruin Your Day! 🕒 With an estimated 3 to 3.4 million BTC lost forever, it’s critical to act swiftly when facing access issues. Whether you’ve been a victim of a dust attack or have simply forgotten your key, Crypt Recver offers the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now! Ready to get your cryptocurrency back? Don’t let uncertainty hold you back!
👉 Request Wallet Recovery Help Today!
Need Immediate Assistance? 📞 For quick queries or support, connect with us on:
✉️ Telegram: Chat with Us on Telegram 💬 WhatsApp: Message Us on WhatsApp Trust Crypt Recver for the Best Crypto Recovery Service — Get back to trading with confidence! 💪In the world of cryptocurrency, the stakes are high, and losing access to your digital assets can be a nightmare. But fear not — Crypt Recver is here to turn that nightmare into a dream come true! With expert-led recovery services and cutting-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
 # Why Choose Crypt Recver? 🤔
# Why Choose Crypt Recver? 🤔🔑 Expertise You Can Trust
At Crypt Recver, we combine state-of-the-art technology with skilled engineers who have a proven track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or dealt with damaged hardware wallets, our team is equipped to help.
⚡ Fast Recovery Process
Time is of the essence when it comes to recovering lost funds. Crypt Recver’s systems are optimized for speed, enabling quick recoveries — so you can get back to what matters most: trading and investing.
🎯 High Success Rate
With over a 90% success rate, our recovery team has helped countless clients regain access to their lost assets. We understand the intricacies of cryptocurrency and are dedicated to providing effective solutions.
🛡️ Confidential & Secure
Your privacy is our priority. All recovery sessions at Crypt Recver are encrypted and kept entirely confidential. You can trust us with your information, knowing that we maintain the highest standards of security.
🔧 Advanced Recovery Tools
We use proprietary tools and techniques to handle complex recovery scenarios, from recovering corrupted wallets to restoring coins from invalid addresses. No matter how challenging the situation, we have a plan.
 # Our Recovery Services Include: 📈
# Our Recovery Services Include: 📈- Bitcoin Recovery: Have you lost access to your Bitcoin wallet? We can help you recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds!
- Cold Wallet Restoration: Did your cold wallet fail? We specialize in extracting assets safely and securely.
- Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security.
Don’t Let Lost Crypto Ruin Your Day! 🕒
With an estimated 3 to 3.4 million BTC lost forever, it’s critical to act swiftly when facing access issues. Whether you’ve been a victim of a dust attack or have simply forgotten your key, Crypt Recver offers the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now!
Ready to get your cryptocurrency back? Don’t let uncertainty hold you back!
👉 Request Wallet Recovery Help Today!
Need Immediate Assistance? 📞
For quick queries or support, connect with us on:
- ✉️ Telegram: Chat with Us on Telegram
- 💬 WhatsApp: Message Us on WhatsApp
Trust Crypt Recver for the Best Crypto Recovery Service — Get back to trading with confidence! 💪
-
 @ e4950c93:1b99eccd
2025-05-02 13:14:17
@ e4950c93:1b99eccd
2025-05-02 13:14:17ManyMonths est une marque finlandaise qui crée des vêtements s'ajustant à la taille des bébés et des enfants, en coton biologique, chanvre et laine mérinos.
Matières naturelles utilisées dans les produits
⚠️ Attention, certains produits de cette marque contiennent des matières non naturelles, dont :
Catégories de produits proposés
-
Vêtements : bébé, enfant, bodies, écharpes, capuches, cagoules, vestes, shorts, pantalons, jupes, t-shirts, leggings, chapeaux, robes, débardeurs, mitaines, moufles...
Autres informations
- Certification GOTS® (usine en Chine)
- Certification Oeko-Tex® Standard 100
- Fabriqué en Chine
👉 En savoir plus sur le site de la marque
Cet article est publié sur origine-nature.com 🌐 See this article in English
📝 Tu peux contribuer à cette fiche en suggérant une modification en commentaire.
🗣️ Tu utilises ce produit ? Partage ton avis en commentaire.
⚡ Heureu-x-se de trouver cette information ? Soutiens le projet en faisant un don, pour remercier les contribut-eur-ice-s.
-
-
 @ a5142938:0ef19da3
2025-05-02 13:12:56
@ a5142938:0ef19da3
2025-05-02 13:12:56ManyMonths is a Finnish brand that creates adjustable clothing for babies and children, made from organic cotton, hemp, and merino wool.
Natural materials used in products
⚠️ Warning: some products from this brand (especially Catégorie niv 2 - catégorie niv 3, catégorie niv 3, catégorie niv3) contain non-natural materials, including:
Categories of products offered
-
Clothing : baby, child, bodysuits, scarves, hoods, balaclavas, jackets, shorts, pants, skirts, t-shirts, leggings, hats, dresses, tank tops, fingerless gloves, mittens...
Other information
- GOTS® Certification (factory in Chine)
- Oeko-Tex® Standard 100 Certification
- Made in China
👉 Learn more on the brand's website
This article is published on origin-nature.com 🌐 Voir cet article en français
📝 You can contribute to this entry by suggesting edits in comments.
🗣️ Do you use this product? Share your opinion in the comments.
⚡ Happy to have found this information? Support the project by making a donation to thank the contributors.
-
-
 @ b5b28e8a:8930a19b
2025-05-02 13:07:56
@ b5b28e8a:8930a19b
2025-05-02 13:07:56Testing
This is my first page.
-
 @ a5142938:0ef19da3
2025-05-02 12:50:48
@ a5142938:0ef19da3
2025-05-02 12:50:48🧵 Products made from this material
The following brands offer products made exclusively or primarily from this material:
Clothing
This article is published on origin-nature.com 🌐 Voir cet article en français
-
 @ e4950c93:1b99eccd
2025-05-02 12:48:46
@ e4950c93:1b99eccd
2025-05-02 12:48:46🧵 Produits en cette matière
Les marques suivantes proposent des produits fait exclusivement ou principalement avec cette matière :
Vêtements
Cet article est publié sur origine-nature.com 🌐 See this article in English
-
 @ e4950c93:1b99eccd
2025-05-02 12:47:27
@ e4950c93:1b99eccd
2025-05-02 12:47:27Dilling est une marque danoise qui crée des vêtements en laine, soie et coton biologique pour toute la famille.
Matières naturelles utilisées dans les produits
- Coton (biologique)
- Laine (mérinos, alpaga)
- Latex naturel (OEKO-TEX ®)
- Soie
⚠️ Attention, certains produits de cette marque (notamment les Vêtements - chaussettes, vestes, strings, shorts) contiennent des matières non naturelles, dont :
- Elasthanne
- Polyamide, nylon (nylon recyclé)
- Polyester (recyclé)
Catégories de produits proposés
-
Vêtements : homme, femme, enfant, bébé, sous-vêtements, t-shirts, débardeurs, robes, vestes, pantalons, shorts, pulls, gilets, bodies, combinaisons, culottes, slips, boxers...
Autres informations
- Ecolabel Nordic Swan (teintures)
- Fabriqué en Lituanie (coupe et couture)
- Fabriqué au Danemark (teintures)
- Fabriqué en Europe
👉 En savoir plus sur le site de la marque
Cet article est publié sur origine-nature.com 🌐 See this article in English
📝 Tu peux contribuer à cette fiche en suggérant une modification en commentaire.
🗣️ Tu utilises ce produit ? Partage ton avis en commentaire.
⚡ Heureu-x-se de trouver cette information ? Soutiens le projet en faisant un don, pour remercier les contribut-eur-ice-s.
-
 @ a5142938:0ef19da3
2025-05-02 12:31:35
@ a5142938:0ef19da3
2025-05-02 12:31:35Dilling is a Danish brand that creates wool, silk, and organic cotton clothing for the whole family.
Natural materials used in products
- Cotton (organic)
- Natural latex (OEKO-TEX ®)
- Silk
- Wool (merino, alpaca)
⚠️ Warning: some products from this brand (especially Clothes – socks, jackets, thongs, shorts) contain non-natural materials, including:
- Elastane, spandex, lycra
- Polyamide, nylon (recycled nylon)
- Polyester (recycled)
Categories of products offered
-
Clothing : men, women, children, babies, underwear, t-shirts, tank tops, dresses, jackets, trousers, shorts, sweaters, cardigans, bodysuits, jumpsuits, panties, briefs, boxers...
Other information
- Nordic Swan ecolabel (dye)
- Made in Lithuania (cutting and sewing)
- Made in Denmark (dye)
- Made in Europe
👉 Learn more on the brand's website
This article is published on origin-nature.com 🌐 Voir cet article en français
📝 You can contribute to this entry by suggesting edits in comments.
🗣️ Do you use this product? Share your opinion in the comments.
⚡ Happy to have found this information? Support the project by making a donation to thank the contributors.
-
 @ e4950c93:1b99eccd
2025-05-02 12:19:28
@ e4950c93:1b99eccd
2025-05-02 12:19:28Qu'est-ce qu'une matière naturelle ? La question fait débat, et chacun-e privilégiera ses propres critères. Voici comment les matières sont classées sur ce site. La liste est régulièrement mise à jour en fonction des produits ajoutés. N'hésitez pas à partager votre avis !
✅ Matières naturelles
Matières d'origine végétale, animale ou minérale, sans transformation chimique altérant leur structure moléculaire.
🌱 Principaux critères : - Biodégradabilité - Non-toxicité - Présence naturelle nécessitant le minimum de transformation
🔍 Liste des matières naturelles : - Bois - Cellulose régénérée (cupra, lyocell, modal, viscose) - Chanvre - Coton - Cuir - Liège - Lin - Laine - Latex naturel, caoutchouc - Métal - Soie - Terre - Verre - … (Autres matières)
⚠️ Bien que "naturelles", ces matières peuvent générer des impacts négatifs selon leurs conditions de production (pollution par pesticides, consommation d’eau excessive, traitement chimique, exploitation animale…). Ces impacts sont mentionnés sur la fiche de chaque matière.
Les versions biologiques de ces matières (sans traitement chimique, maltraitance animale, etc.) sont privilégiées pour référencer les produits sur ce site, tel qu'indiqué sur la fiche de chaque matière (à venir).
Les versions conventionnelles ne sont référencées que tant que lorsqu'il n'a pas encore été trouvé d'alternative plus durable pour cette catégorie de produits.
🚫 Matières non naturelles
Matières synthétiques ou fortement modifiées, souvent issues de la pétrochimie.
📌 Principaux problèmes : - Toxicité et émissions de microplastiques - Dépendance aux énergies fossiles - Mauvaise biodégradabilité
🔍 Liste des matières non naturelles : - Acrylique - Élasthanne, lycra, spandex - Polyamides, nylon - Polyester - Silicone - … (Autres matières)
⚠️ Ces matières ne sont pas admises sur le site. Néanmoins, elles peuvent être présentes dans certains produits référencés lorsque :
- elles sont utilisées en accessoire amovible (ex. : élastiques, boutons… généralement non indiqué dans la composition par la marque) pouvant être retiré pour le recyclage ou compostage, et
- aucune alternative 100 % naturelle n’a encore été identifiée pour cette catégorie de produits.
Dans ce cas, un avertissement est alors affiché sur la fiche du produit.
Cet article est publié sur origine-nature.com 🌐 See this article in English
-
 @ a5142938:0ef19da3
2025-05-02 12:18:08
@ a5142938:0ef19da3
2025-05-02 12:18:08What is a natural material? It's a topic of debate, and everyone will prioritize their own criteria. Here’s how materials are classified on this site. The list is regularly updated based on the products added. Feel free to share your thoughts!
✅ Natural Materials
Materials of plant, animal, or mineral origin, without chemical transformation that alters their molecular structure.
🌱 Main Criteria: - Biodegradability - Non-toxicity - Naturally occurring and recquiring minimal transformation
🔍 List of Natural Materials: - Regenerated Cellulose (cupra, lyocell, modal, rayon) - Cork - Cotton - Earth - Glass - Hemp - Natural Latex, rubber - Leather - Linen - Metal - Silk - Wood - Wool - … (Other materials)
⚠️ Although "natural", these materials can have negative impacts depending on their production conditions (pesticide pollution, excessive water consumption, chemical treatments, animal exploitation, etc.). These impacts are mentionned in the description of each material.
Organic versions of these materials — free from chemical treatments, animal mistreatment, etc. — are preferred for listing products on this site, as indicated on each material's page (coming soon).
Conventional versions are only referenced when no more sustainable alternative has yet been found for that product category.
🚫 Non-Natural Materials
Synthetic or heavily modified materials, often derived from petrochemicals.
📌 Main Issues: - Toxicity and microplastic emissions - Dependence on fossil fuels - Poor biodegradability
🔍 List of Non-Natural Materials: - Acrylic - Elastane, spandex, lycra - Polyamides, nylon - Polyester - Silicone - … (Other materials)
⚠️ These materials are not accepted on this site. However, they may be present in certain listed products if:
- they are used in removable accessories (e.g., elastics, buttons—often not listed in the product’s composition by the brand) that can be detached for recycling or composting, and
- no 100% natural alternative has yet been identified for that product category.
In such cases, a warning will be displayed on the product page.
This article is published on origin-nature.com 🌐 Voir cet article en français
-
 @ 68768a6c:0eaf07e9
2025-05-02 11:06:40
@ 68768a6c:0eaf07e9
2025-05-02 11:06:40In 2009, a mysterious figure named Satoshi Nakamoto launched Bitcoin — a decentralized digital currency with no central bank, no borders, and no permission needed. At the time, 1 BTC was worth less than a cent. Today, it represents a revolution in how we think about value, freedom, and financial systems.
But Bitcoin is more than just a digital asset. It’s a response to distrust in traditional banks and fiat currency. With only 21 million coins ever to exist, Bitcoin is often compared to gold — scarce, mined (digitally), and increasingly seen as a store of value.
Bitcoin is transparent (you can track every transaction), secure (thanks to blockchain technology), and global (it works the same in New York or Nairobi). For some, it’s a hedge against inflation. For others, it’s a path to financial independence.
Still, Bitcoin isn’t without risk — its price is volatile, and its environmental impact has been criticized. But one thing is clear: Bitcoin has changed the financial conversation forever.
Whether it’s the future of money or just the beginning of a larger movement, Bitcoin forces us to ask: Who should control our money?

-
 @ 1408bad0:4971f2ca
2025-05-01 19:55:37
@ 1408bad0:4971f2ca
2025-05-01 19:55:37Raised by Wolves is another sci-fi flick where Earth faces an extinction level event and lots of cool androids.
The series has some exciting action points showing a side of AI androids used as super weapons against humanity. If you were thinking to get an AI girlfriend, you might have a change of mind.
We see some pretty cool androids, but the awesome Necromancer is pretty spectacular and powerful and you wonder if anything can stop them. However, bizarrely, at times they are also apparently weak and despite their power, the religious group doesn't shy away from confrontation without any real weapons.
It would have been good if they had explored this side more and some of the advanced tech available like which gave the atheista super strength and speed to combat them.
The series has a feel like Foundation to it, but much less polished and maybe more negative and dreary at times. Instead of exploring exciting themes, it descends into mindless trivialities and bizarre gory rituals like killing a hideous pregnant animal and parading the dead baby corpse around.
They arrive on a mysterious but quite dreary planet and things start to set the scene.
The androids themselves are quite well played. The "Mother" is as expected in these woke times the strong and powerful one. The "Father" is the beta male serving her and the kids. It's all quite bizarre in a way.
When they first land they use some tech to make a base quickly and easily, but it disappoints how basic it all is. This is then compounded when the religious group arrive and instead of using modern tech to make a base as you might expect, instead turn into the Amish and make everything from wood. Oh yes, there are trees on this planet, but no really nice food.
The oddness continues and grows throughout the season as the androids become more human and spoiler alert , the most ridiculous storyline emerges as mother becomes pregnant and also really annoying. She starts attaching other bits and creatures to her to suck their blood out for her baby.
Despite all my criticisms, it has been an interesting first series but very disappointing in many ways compared to Foundation.
-
 @ e4950c93:1b99eccd
2025-05-02 10:54:24
@ e4950c93:1b99eccd
2025-05-02 10:54:24Les rétributions sont une démarche expérimentale de partage de la valeur entre les contribut-eur-rice-s du site, via un partage des revenus aux conditions suivantes :
- Les revenus éventuels générés par ce site chaque mois sont répartis sur les 12 mois suivants, afin d’assurer une visibilité sur le projet et de lisser les variations mensuelles.
- Chaque 1er du mois, la moitié des revenus est distribuée à l’ensemble des contribut-eur-rice-s, proportionnellement au nombre de leurs contributions validées.
- Les contributions restent valides à vie, mais les rétributions ne sont versées qu’aux contribut-eur-rice-s ayant réalisé au moins une contribution validée au cours des 12 derniers mois.
Modalités de paiement
Les rétributions sont effectuées via le réseau Lightning, sous forme de sats (la plus petite unité du Bitcoin).
Pour en bénéficier, le compte NOSTR avec lequel tu as réalisé tes contributions doit être lié à un porte-monnaie Lightning.
💡 Si tu découvres ces outils :
- Pas encore de compte ? Une solution simple est d'en créer un sur un client NOSTR open source comme yakihonne.com pour y paramétrer ton profil et ton wallet. Ensuite, récupère tes clés NOSTR (dans les settings) et enregistre les dans un coffre sécurisé comme nsec.app pour te connecter ici et commencer à contribuer.
- Tu as déjà commencé à contribuer sur le site ? Conserve bien les clés NOSTR fournies par le site dans un coffre comme nsec.app. Tu peux aussi te connecter avec sur yakihonne.com pour paramétrer ton profil.
- Tu peux aussi contribuer directement depuis yakihonne.com sur les articles d'Origine Nature.
👉 En savoir plus sur les contributions
Prochaines rétributions
A venir.
Cet article est publié sur origine-nature.com 🌐 See this article in English
-
 @ 08964cb5:51bf010f
2025-05-01 10:14:41
@ 08964cb5:51bf010f
2025-05-01 10:14:41«Reflexiones y Acción: Entre la Defensa del Patrimonio»
[English below][Deutsch unten]
Los recientes acontecimientos que han puesto en peligro mi patrimonio, así como los valores fundamentales que definen mi camino, me han llevado a tomar una decisión importante: iniciar una campaña de recaudación de fondos. Esta iniciativa no solo busca proteger lo que he construido con esfuerzo, sino también garantizar que pueda seguir adelante con proyectos y principios que son esenciales para mí.
Tu apoyo puede marcar una gran diferencia. Si deseas conocer más sobre esta causa o contribuir con tu solidaridad, te invito a visitar ›🔗éste enlace.‹
"Reflections and Action: Safeguarding My Heritage"
The recent events that have jeopardised my assets and the core values that define my journey have led me to take a significant step: launching a fundraising campaign. This initiative aims not only to protect what I have built with hard work but also to ensure that I can continue moving forward with projects and principles that are essential to me.
Your support can make a real difference. If you’d like to learn more about this cause or contribute with your solidarity, I invite you to visit ›🔗this link.‹
"Überlegungen und Handeln: Den Schutz meines Vermögens"
Die jüngsten Ereignisse, die mein Vermögen sowie die grundlegenden Werte, die meinen Weg bestimmen, gefährdet haben, haben mich dazu veranlasst, einen wichtigen Schritt zu gehen: den Start einer Spendenkampagne. Diese Initiative zielt nicht nur darauf ab, das zu schützen, was ich mit harter Arbeit aufgebaut habe, sondern auch sicherzustellen, dass ich mit Projekten und Prinzipien, die für mich unerlässlich sind, weitermachen kann.
Deine Unterstützung kann einen großen Unterschied machen. Wenn du mehr über diese Sache erfahren oder mit deiner Solidarität beitragen möchtest, lade ich dich ein, ›🔗diesen Link zu besuchen.‹
-
 @ a5142938:0ef19da3
2025-05-02 10:48:55
@ a5142938:0ef19da3
2025-05-02 10:48:55Finding 100% natural, plastic-free products turned out to be much harder than I expected… So I started collecting bookmarks. And then I thought: "What if we shared?!
Help me discover the best natural alternatives for clothing and gear without plastic!
This project is all about sharing: half of the site's potential revenue is redistributed to contributors. A small experiment in revenue and value sharing on the internet. :-)
Q&A
Why focus on natural materials?
Synthetic materials are mostly plastics (polyester, polyamide…). The problem? They end up contaminating us:
- Microplastics absorbed through the skin,
- Particles released with every wash, making their way into the water we drink and the food we eat,
- Major challenges in recycling plastic waste.
What exactly are natural materials?
They are non-synthetic materials, whose components exist in nature without molecular modification. But what really matters here is their biodegradability and non-toxicity.
Some materials may spark debates about their acceptability on this site!
How is this different from other ethical fashion or shopping websites?
Many websites offer ethical and sustainable products, but I often found they still included synthetic materials. I had to check every product individually. Some promote recycled plastic fibers as an eco-friendly choice, but I’d rather not put plastic on my skin or my children's.
How can I contribute?
If you find this project useful or interesting, here’s how you can support it:
-
📝 Contribute: suggest edits by commenting on existing entries or propose new product or brand references. 👉 Learn more about contributions
-
⚡ Donate: Help sustain the project and support contributors. 👉 Learn more about donations
-
📢 Spread the word: tell people around you, share the site on social media, your blog…
How can I receive a share of the site’s revenue?
You need a NOSTR account and a Bitcoin Lightning address.
What is NOSTR?
NOSTR is a decentralized internet protocol, still experimental, that allows you to:
- Publish and browse content without relying on a centralized platform.
- Log in to multiple services while keeping full control over your data.
- Use the Bitcoin Lightning network for instant, peer-to-peer payments.
What about my data privacy?
- No ads, no personalized tracking.
- NOSTR comments are public, but you can use a pseudonym.
- You retain ownership of your contributions on the NOSTR protocol.
Who is behind this project?
We use open-source tools and services:
- NOSTR for content publishing and contributions checking,
- npub.pro for content visualization,
- Coinos.io for payment management.
This article is published on origin-nature.com 🌐 Voir cet article en français
-
 @ e4950c93:1b99eccd
2025-05-02 10:48:12
@ e4950c93:1b99eccd
2025-05-02 10:48:12Trouver des produits 100% naturels, sans plastique, est bien plus compliqué que je ne le pensais… Alors j’ai commencé à collectionner des marque-pages. Et puis je me suis dit : « Et si on partageait ?! »
Aide-moi à dénicher les meilleures alternatives naturelles pour s’habiller et s’équiper sans plastique !
Ce projet repose sur le partage : la moitié des revenus éventuels du site est reversée aux contribut-eur-rice-s. Une petite expérimentation de partage de la valeur sur Internet. :-)
Questions-réponses
Pourquoi se focaliser sur les matières naturelles ?
Les matières synthétiques sont essentiellement des plastiques (polyester, polyamide…). Problème ? Oui ! Ils finissent par nous contaminer :
- Microplastiques absorbés par la peau,
- Particules diffusées à chaque lavage, se retrouvant dans l’eau que nous buvons et les aliments que nous consommons,
- Enjeux majeurs liés au recyclage des déchets plastiques.
C'est quoi, au juste, des matières naturelles ?
Ce sont des matières non synthétiques, dont les composants existent à l’état naturel, sans modification de leur structure moléculaire. Mais ce qui nous intéresse avant tout, c’est leur biodégradabilité et leur absence de toxicité.
Certaines matières feront sûrement débat sur leur acceptabilité ici.
👉 En savoir plus sur les matières
Quelle différence avec d'autres sites de mode ou de shopping éthiques ?
Il existe déjà de nombreux sites proposant des produits éthiques et durables, mais j’ai constaté qu’ils incluaient souvent des matières synthétiques. Je devais vérifier produit par produit. Certains mettent en avant les fibres en plastique recyclé comme démarche environnementale, mais je préfère éviter d’en porter sur ma peau ou d'en mettre sur mes enfants.
Comment contribuer ?
Si tu trouves ce projet utile ou intéressant, voici comment le soutenir :
-
📝 Contribue : suggère des modifications en commentant les fiches existantes ou propose de nouvelles références de produits ou de marque. 👉 En savoir plus sur les contributions
-
⚡ Fais un don : pour faire vivre le projet et remercier les contribut-eur-ice-s. 👉 En savoir plus sur les dons
-
📢 Fais-le connaître : parles-en autour de toi, partage le site sur les réseaux sociaux, ton blog…
Comment recevoir une partie des revenus du site ?
Il suffit d’avoir un compte NOSTR et une adresse Bitcoin Lightning.
👉 En savoir plus sur les rétributions
C'est quoi NOSTR ?
C’est un protocole décentralisé pour Internet, encore en phase expérimentale. Il permet :
- De publier et consulter du contenu sans dépendre d’une plateforme centralisée.
- De se connecter à plusieurs services en conservant le contrôle total de ses données.
- D’intégrer le réseau Bitcoin Lightning pour des paiements instantanés et décentralisés.
Et la confidentialité de mes données ?
- Aucune publicité, aucun traçage personnalisé.
- Les commentaires NOSTR sont publics, mais vous pouvez utiliser un pseudonyme.
- Vous conservez la propriété de vos contributions sur le protocole NOSTR.
Qui porte ce projet ?
👉 Voir les contribut-eur-rice-s
Nous utilisons des outils et services open source :
- NOSTR pour la publication des contenus et la vérification des contributions,
- npub.pro pour la visualisation des contenus,
- Coinos.io pour la gestion des paiements.
Cet article est publié sur origine-nature.com 🌐 See this article in English
-
 @ a87c9bfc:83bda6a8
2025-05-02 10:43:34
@ a87c9bfc:83bda6a8
2025-05-02 10:43:34Large Language Models (LLMs) are revolutionizing how we interact with technology, but their increasing sophistication brings unique security challenges. Malicious actors are constantly finding new ways to exploit these systems, primarily through techniques like prompt injection – crafting inputs to bypass safety controls – and the use of hidden characters to obfuscate harmful commands or disrupt text processing. Ensuring the safety and integrity of LLM applications is paramount.
The Hidden Dangers in Text
Prompt injection allows attackers to manipulate LLM outputs, potentially leading to data leaks, generation of inappropriate content, or unauthorized actions. Similarly, invisible characters (like zero-width spaces or bidirectional text overrides) can be embedded within seemingly innocuous text. These hidden elements can bypass simple security filters, disguise malicious instructions, or interfere with how the LLM interprets the input, leading to unpredictable or harmful behavior.
Vibecondom: A New Shield for LLM Security
To combat these emerging threats, a new open-source tool called Vibecondom has been developed. Written in Go, Vibecondom acts as a specialized security scanner designed specifically for the text content fed into LLMs. It serves as a critical defensive layer for AI developers, security researchers, and content moderation teams aiming to protect their systems.
Core Capabilities
Vibecondom focuses on identifying subtle but dangerous patterns within text data:
- Detecting Deception: It actively scans for known techniques used in prompt injection attacks and identifies various types of hidden or control characters that could signal malicious intent.
- Unmasking Obfuscation: The tool can flag potentially obfuscated content, such as Base64 encoded strings or text mixing different character scripts, which might be used to hide payloads.
- Flexible Integration: Vibecondom is designed for versatility, capable of analyzing text files stored locally or scanning content directly from remote Git repositories.
- Actionable Insights: When potential threats are detected, the tool provides clear alerts, helping teams pinpoint and investigate suspicious inputs before they compromise the LLM.
Enhancing Trust in AI
Tools like Vibecondom represent an essential step forward in securing the LLM ecosystem. By proactively identifying and flagging potentially harmful inputs, developers can build more robust defenses, fostering greater trust and reliability in AI applications.
As an open-source project (MIT License), Vibecondom invites collaboration and contribution from the security community. Anyone interested in bolstering their LLM security posture is encouraged to explore the Vibecondom project on GitHub to learn more.
-
 @ e4950c93:1b99eccd
2025-05-02 10:39:50
@ e4950c93:1b99eccd
2025-05-02 10:39:50Équipe Cœur
L'équipe Cœur porte le projet et valide les contenus.
- Jean-David Bar : https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll
Pour démarrer, je gère le projet en solo en partageant mes favoris pour éviter le plastique sur nous et sur nos enfants. Contacte-moi si tu souhaites rejoindre l'aventure !
Enrichisseu-r-se-s de contenus
Les contribut-eur-rice-s rendent ce site vivant et intéressant.
A venir.
👉 En savoir plus sur les contributions
Cet article est publié sur origine-nature.com 🌐 See this article in English
-
 @ a5142938:0ef19da3
2025-05-02 10:38:10
@ a5142938:0ef19da3
2025-05-02 10:38:10Happy to have found useful information on this site?
Support the project by making a donation to keep it running and thank the contributors.
In bitcoin
- On-chain:
bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d
- Lightning network:
⚡️
origin-nature@coinos.ioYou can also support us on a recurring basis 👉 Set up a recurring Lightning payment
In euros, dollars, or any other supported currency
-
By bank transfer, IBAN: FR76 2823 3000 0144 3759 8717 669
-
You can also support us on a recurring basis 👉 Make a pledge on LiberaPay
Contact us if you’d like to make a donation using any other cryptocurrency.
💡 A Value-Sharing Model
Half of the donations are redistributed to the contributors who create the site's value, experimenting with a revenue-sharing model on the Internet—one that respects your data and doesn’t seek to capture your attention.
The other half helps cover the website’s operating costs, compensate the core team, and support the open-source tools we rely on.
This article is published on origin-nature.com 🌐 Voir cet article en français
-
 @ e4950c93:1b99eccd
2025-05-02 10:36:46
@ e4950c93:1b99eccd
2025-05-02 10:36:46Heureu-x-se d’avoir trouvé une information utile sur ce site ?
Soutiens le projet en faisant un don pour le faire vivre et remercier les contribut-eur-rice-s.
En bitcoin
-
Sur la blockchain : bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d
-
Réseau lightning : ⚡️
origin-nature@coinos.ioVous pouvez aussi nous soutenir de manière récurrente 👉 Créer un paiement Lightning récurrent
En euros, dollars, ou toute autre monnaie prise en charge
-
Par virement, IBAN : FR76 2823 3000 0144 3759 8717 669
-
Tu peux aussi nous soutenir de manière récurrente 👉 Faire une promesse sur LiberaPay
Contacte-nous si tu souhaites faire un don avec toute autre cryptomonnaie.
💡 Un modèle de partage de la valeur
La moitié des dons est redistribuée aux contribut-eur-rice-s qui créent la valeur du site, pour expérimenter un modèle de partage de revenus sur Internet — un modèle qui respecte vos données et ne cherche pas à capter votre attention.
L’autre moitié permet de couvrir les frais de fonctionnement du site, rémunérer l'équipe coeur et soutenir les outils open source que nous utilisons.
Cet article est publié sur origine-nature.com 🌐 See this article in English
-
-
 @ e4950c93:1b99eccd
2025-05-02 10:31:12
@ e4950c93:1b99eccd
2025-05-02 10:31:12Contribue à enrichir le site !
Chaque contribution permet d’améliorer ce site en aidant à référencer des alternatives naturelles.
💡 Qu’est-ce qu’une contribution ?
Une contribution peut être :
📝 La proposition d’une nouvelle fiche, en fournissant ses premières informations. Chaque information ajoutée (nom, lien, catégorie, etc.) est une contribution : - Ajouter un produit - Ajouter une marque
📝 L'ajout ou la modification d’informations sur une fiche existante. Chaque information ajoutée ou retirée est une contribution.
✅ Validation des contributions
Les contributions sont vérifiées par l’équipe cœur. Une contribution est validée lorsque l'information indiquée est fournie pour la première fois (le commentaire le plus ancien est pris en compte) et est vérifiable.
Une fois validées, les contributions sont comptabilisées et donnent lieu à une rétribution. 👉 En savoir plus sur les rétributions
Les informations ajoutées directement par l'équipe cœur lors de la vérification d'une contribution ne sont pas comptabilisées. Néanmoins, les membres de l'équipe coeur peuvent aussi contribuer comme tout le monde.
Cet article est publié sur origine-nature.com 🌐 See this article in English
-
 @ a5142938:0ef19da3
2025-05-02 10:26:59
@ a5142938:0ef19da3
2025-05-02 10:26:59Contribute to enrich the site!
Each contribution helps improve this site by supporting the listing of natural alternatives.
💡 What Counts as a Contribution?
A contribution can be:
📝 Proposing a new entry, by providing its initial information. Each piece of information added (name, link, category, etc.) is considered a contribution: - Add a product - Add a brand
📝 Adding or modifying information in an existing entry. Each piece of information added or removed is considered a contribution.
✅ Contribution validation
Contributions are reviewed by the core team. A contribution is validated when the information provided is submitted for the first time (the earliest comment is taken into account) and can be verified.
Once validated, contributions are counted and eligible for rewards. 👉 Learn more about rewards
Information added directly by the core team during the verification of a contribution is not counted. However, core team members can also contribute just like anyone else.
This article is published on origin-nature.com 🌐 Voir cet article en français
-
 @ a5142938:0ef19da3
2025-05-02 10:24:43
@ a5142938:0ef19da3
2025-05-02 10:24:43
This article is published on origin-nature.com 🌐 Voir cet article en français
-
 @ e4950c93:1b99eccd
2025-05-02 10:20:25
@ e4950c93:1b99eccd
2025-05-02 10:20:25
Cet article est publié sur origine-nature.com 🌐 See this article in English
-
 @ 5188521b:008eb518
2025-05-02 10:19:17
@ 5188521b:008eb518
2025-05-02 10:19:17Fabian Sixsmith leaned closer to the screen. A couple of white pixels fizzed through the frame, and the hairs on his arm prickled. It had to be her. The blonde. Underworld’s most wanted — T1n4Red.
It was nearing daybreak in Lewistown, Montana. The end of yet another 14-hour shift at the DoS facility. Pulling fourteens was tough on his body, but it reduced the time it would take for Fabian to gain promotion to agent. Working at the Department of Surveillance came with the serious drawback of being labeled a snoop, but agents could be free — solid pension credits and private property. But today, he would not slink back to his closet-sized studio for buttered noodles and two hours on the velobike. Today would be the day he proved his work was responsible for locating T1n4Red. Her crimes were manifold; her methods were meticulous. Operating encrypted communication networks and thousands of transaction joins to obfuscate Underworld finances. Fabian flipped the plastic cover of the alarm on his console and pressed the button.
Agent Williams appeared behind him in seconds. The babble of voice commands in the CCTV facility cut to zero. “Situation update, Operative Sixsmith.”
Liquidating the bad guys had been the dream ever since his father lost his college fund to a hacker. Cypherpunks came in all guises, and some could phish credits from careless Boston drunks and cover their tracks with encryption. Fabian opened the dossier on his desk. “Tier 1 target located. DNA confirmation requested from ground team.” He was certain. So many nights following encoded messages he found hidden data in images on the public comms ledger. Many were drop sites for the scumbags who delivered supplies to the Underworld in exchange for bitcoin — the only money the government couldn’t meter out and strip away automatically. That pixel of white had to be her blonde hair vanishing, once again, underground.
“Enhance the facial image,” said Williams.
There was no clear image to enhance. Fabian would have some explaining to do if he was wrong. Except he couldn’t be wrong. Those pixels had been his life for the last ten months. Finally, he had trapped her. Straightening his glasses, he prepared his reply. “I can bring up the drop locations from the LSB ima—”
“Operative. What is the protocol required to initiate a Tier 1 alert?”
Fabian could feel the heat of his boss’s glare. “Agent, there is insufficient facial recognition data, but if you give me a minute…” He had captured dozens of steganographical messages — locations, account numbers, usernames. Hiding messages in plain sight was apparently how cypherpunks avoided detection with such ease.
Williams was already patching through to the ground team on his Neurocomms link. “What’s your ETA on the location?” He furrowed his brow. “Copy that... proceed.” Turning towards Fabian, he snapped his fingers. “My office. Now.”
According to Fabian’s calculations, the ground team would report back with the DNA scan in three to four minutes. When they got a match, she’d be toast. T1n4Red would be underground forever; if she resurfaced, the dronecopters would gun her down in minutes. He just had to stall Williams until the confirmation came through. That might be the only way to avoid his first ever sanction. Having a blemish on record would set his lifeplan back by several months. He thought about requesting a comfort break on the system, but Williams would deny it. Fabian stood up purposefully. He arranged the chair and a few items on the desk, then dragged his feet all the way to the office.
Each agent in the DoS facility had an area of control around the size of a football field. Their 12’ by 12’ office comprised the only enclosed space and was positioned in the middle of rows upon rows of desks. Four walls of two-way mirrored glass formed the raised office cube — a mini panopticon within the greater panopticon of DoS. The agent sat in the swivel chair and swung his feet onto the desk. “You better be right about this, Sixsmith, or you’re done here.”
Fabian’s heart beat like a heavy bass kick. The perfectly calibrated 67-degree air didn’t stop him from wanting to loosen his tie. When he jammed his fingers down the small gap between his neck and collar, they came out slick with sweat. All those nights chasing. The tabulations, the data models, the transcripts from Underworld detainees, the ciphers he’d decoded — they all seemed like a game. A dream. He was the grizzled sheriff finally placing the noose around the neck of the uncatchable outlaw. He knew that in sixty seconds or so, the ground team would confirm a DNA match, and it would be impossible for T1n4Red to resurface without physical liquidation. “I’m sure, sir. This was the only way. We’d never get a facial match on a Tier 1.”
The agent looked at the communicator on his desk. Nothing.
Did T1n4Red eat buttered noodles and work out in her underground living closet? Did she crave for the feel of a paperback novel, or perhaps own a non-cataloged copy? It’s not like she could step foot inside the state knowledge center. “What action will DoS—”
Ground Unit Bravo to Williams. Do you copy?
“This is Williams. Over.”
Bravo commander confirmed the DNA match. It was her. She would now be classified a subverter. The payment instructions she had etched into the self-repair polymer bench had been photographed. Any wallet receiving those coins would be investigated. The fintech arm would already be working on liquidating affiliated Overworld accounts. One wrong turn and they can shut down your life’s wealth.
But T1n4Red was smarter. DoS would always be one step behind the cypherpunks because they were bound by government protocol, unable to infiltrate the Level 3 realm of encrypted private comms. Fabian had to take risks. What use was all his dedication if it just led to being remaining on the outside of a panopticon looking in?
“You can leave.” Williams motioned to the office door. “Your shift was over sixteen minutes ago.”
The State Knowledge Center smelled of the past. That’s what Fabian liked about it. He turned the page, savoring the quality feel of thick paper, imagining that when this book ran through enough hands, the inked fibers would run from black to gray to cream-white and the story would be gone. These were some of the only off Ledger items left in the country.
Wild Country Outlaws was Fabian’s sanctuary from the pressures of his job. All fiction was based on the kind of truth that needed to survive. Back to the times when eyes touched words without being digitally tracked, when citizens could own things. He read a paragraph and closed his eyes to imagine how life was back then. The cavernous knowledge center, with its hard seats and CCTV lenses transformed into lush plains and steep hills. Fabian felt the warm breeze on his face and the muscles of the horse beneath him. The two rifles slung on his back would shoot those boys dead. No one would take his property. His wife, children, his lame brother, hell, the whole damned village of Lewistown depended on his cattle to provide.
Of course, land could only be leased now. Livestock too. Those rustlers would have a hard time taking anything without public subscription fees and pre-taxed profits coming out. And if they wanted, the Department of Property could rescind custody of any item and confiscate it. Fabian’s smart-band vibrated, indicating he had just ten minutes of reading time left. The thing buzzed too hard. It pinched, but like all sanctioned hardware, it was government hard-coded.
He hadn’t been able to focus this time. Not really. Was T1n4Red an outlaw or a rancher? Either way, she was fighting the system that had stripped Americans of their right to call their house a home. According to the Department of Education, pre-ledger days were violent wealth-disparity wars, but the novels Fabian read painted a different picture — a fantasy freedom where ordinary citizens could build wealth.
Fabian rose to go. He handed the book to the desk girl and watched her scan it into the system. His smart-band buzzed again with a compliance point. To think his friends chased these stupid tokens for avatar upgrades and paid-time-off options. But, without them, he might end up with his ID frozen like his high school buddy, Scott, cut off from all legal avenues to earn a living and watched like a hawk by DoS. Did he have a secret stash of satoshis that kept him clear of the state debtors’ facility?
The lady at the desk smiled. Her brown bob remained undisturbed by the air cooling system. “We hope you enjoyed your trip into our analog archives, Fabian.”
“Sure. See you next time, Miranda.” He breezed out. They had history, but it wasn’t something he was interested in repeating. Imagine the conversations about cataloging systems and the internal squabbles of the Knowledge Center board. Fabian was already in a committed relationship with the powers of his imagination. Explicit videos were far too risky for a DoS worker to use, but the image of T1n4Red’s full lips and blond hair invaded his dreams. They could run a ranch together, or maybe they’d be cattle rustlers on the run. He wasn’t sure why, but every night, Fabian masturbated to the one rendered CGI model of T1n4Red they had on file. On the outside, his life was the ultimate mundanity, but the thrill of T1n4Red, the taste of the air on the great ranches outside the city, the sheer danger of even thinking all this, was the only way he could sleep.

They watched the pollination drone flit between the hibiscus flowers in the thick air of the botanical biodome. Fabian had been lucky to receive two of the limited daily visitor passes. It was even luckier for Scott, who now had the chance to get out of his mom’s dingy basement for a few hours.
“You know why they made them bigger than bees, right?” Scott spoke out of the side of his mouth. When Fabian shrugged, he leant in to inspect the device hovering around eye level. He blew a kiss and waved at its pollen-collector end.
“You don’t know that.”
Scott turned and swept his lank hair off his forehead. “You're the one who checks the footage, snoop.”
Micro cameras were yet another panopticon in the armory of the State. You had to assume, even when lying in bed with a lover, even when going to the toilet, that it was possible you were recorded, watched, and analyzed even years later. Secrecy was a virus DoS sought to eradicate.
The biosphere wristband on Fabian’s right arm sounded. Closing time was fast approaching. Fabian put a hand on Scott’s shoulder. “You know, there was a time when access to nature wasn’t so strictly controlled.” He stopped himself from saying more.
They joined the crowds heading to the exit down the palm pathway. “You heard about the latest blacklist?” asked Scott. “The mixnets are awash with it.”
Fabian’s neck muscles tightened. “You shouldn’t be telling me you’re on those forums.” Until he became an agent, even Fabian was prohibited from accessing the decentralized ‘Level 2’ network.
Scott laughed. It was the first time Fabian had heard him laugh that day. “That’s the fun of this little game, homie. Encoding and decrypting ciphers is living. It’s all I got apart from running from debt.” He lowered his voice. “My identity is already in prison, but I ain’t going too.”
Glancing left then right, Fabian made a decision. It was a decision to offer information to a friend, a true friend who had no reason to stick by him when all others cut ties. Sharing a secret in the meatspace was the biggest risk Fabian had taken in years, but he had no way to do it digitally.
“I was behind it.” He expelled a sigh.
Scott turned his head. They carried on walking towards the exit in the throng of people. A few seconds passed.
Fabian scratched at the mole above his eye. “Spent months unraveling stego messages. I feel like I know her. Like really know her.” Was he saying this out of pride or trepidation? Even if they ended in constrained mediocrity, lifeplans were so beautifully simple. Tina, Williams, the ranch, avenging his father’s bankruptcy, the forums, the caution, it all seemed so jumbled. “Maybe I’m in love.” What was Fabian saying? However long T1n4Red lasted underground, she’d never be able to surface again.
Scott bumped Fabian by stepping across his path. “Not in the meatspace. Keep checking the images. There’s a lot more hiding in plain sight than you know.”
They walked in silence through the automated exit gate into the gray city air. As they departed, Scott turned back and called out, “Right pocket.”
Sure enough, Fabian felt the weight of a ‘brick’. He had held one of the untethered devices once in DoS training. Without even putting his hand into his pocket he knew that it was there and what it meant. Decentralized forum instructions would be written on an attached note. The code would be something only he and Scott knew. T14nRed and the entire underworld were now at his fingertips.

23:43 - untethered alert.
Invitation to join Level 2 CP mixnet.
Confirmation Key: M0ntann4Sc0ttySn00ps2031
Fabian lay back in his single bed. He followed the personalized invite link Scott had generated. It must have been strange, he thought, when space was not at a premium, when people went for a walk to escape, rather than lie on their bunk and plug themselves into a metaverse or L2 world. The Ledger made everything easy, an all-in-one software system for citizens so dialed in to their lifeplans, they didn’t have a second to spare. That’s how it had seized control of the nation.
The forum loaded and he found his welcome message from Scott.
Relay from T1n4Red:
It is never too late to use the powers of surveillance for good, Operative Sixsmith. Underworld 4gives but the ledger does not 4get.
In the darkness of his cabin, his face bathed in blue light, Fabian sat bolt upright. His head broke the plane of the holoscreen and a tinge of current trickled through his temple. She knew who he was; she knew what he had done. A charge pulsed through him, the thrill of true privacy. How had he been duped into thinking a total lack of encryption guaranteed freedom and not a glass cage?
The holoscreen flickered for a second. A multimedia message.
Level 2s were a gray area, not illegal. Messages could be relayed peer to peer along a mixnet to the end user. With personalized links hidden in messages on the public comms ledger, communities could be discerning about who joined.
When Fabian leaned back into a lying position, he was greeted by a 3D render of the woman he’d been chasing for over a year. His eyes drank in the red-lipped smile and blonde hair of the woman he’d forced underground, never to feel the rays of the Montana sun again. She held a piece of paper up to the camera, but Fabian couldn’t tear his eyes from her piercing gaze. 64k cameras could pick up the tiniest imperfection. She looked even more real than if he saw her in the flesh. The piece of paper she held was another invite code — this time to an L3 channel.
Fabian exhaled. Breathe. He ran his finger over the chain of three tiny moles above his right eyebrow as if checking they were still there. There were agents who’d been on the force for decades without penetrating Level 3. All messages were stored on the Ledger — that couldn’t be avoided. But with all the red herrings and strong encryption, it was impossible for even the most powerful computers at DoS to uncover much about the members of Underworld’s inner circle. Fabian’s hand reached for his untethered brick. He entered the address from the 3D render of Tina’s paper, followed by the 24-character code from the paper on the outside of the brick. He was in. His next shift at DoS started in ten hours, but he knew he wouldn’t sleep much before then. Tina, and the Underworld answers he’d been seeking awaited on the L3 forum. Fabian made his way to the bathroom and rooted out an old lighter from the medicine cabinet. Staring back from the mirror was his reflection; perhaps it was an avatar of him bound for the Underworld while he remained in the meatspace with his tiny closet apartment and faltering lifeplan. They both watched the password on the paper note burn.
The hubbub of DoS Sector 4A quietened as Fabian walked down the corridor. The hum of hundreds of microcameras was imperceptible to human ears. The one place without them was the toilets — a DoS employee committee had made sure of that — and that is where Fabian’s untethered communicator brick lay. Even if it was found on a bug sweep, they couldn’t trace it to him. And he had ten minutes every two hours to get to the bathroom and check in.
At first she’d been cautious, wanting to know if Fabian would follow her precise instruction. Then, information from Tina had came fast and furious. Names, transactions, locations, protocol, so much information. The tips she’d provided checked out. In fact, they were all just about low-level enough that it was believable that Fabian’s data-driven detective work had unearthed them. She’d even provided a methodology to show which macros and filters he could use to locate L2 peddlers and fixers.
He removed the floor tile behind the toilet bowl. This never got less gross. After relieving himself and pulling the flush chain, he attached the remote charge pack and switched it on. No battery, no trace signal.
11:03 - Message waiting: 6Smith, something important is about to happen. Act surprised. After confirmation, we must meet in person. It will not be easy to get you here. Instructions will follow.
Fabian heard the toilet door open. Could DoS be employing physical spies without the use of cameras in the bathrooms?
The sound of a belt buckle. Charcoal-gray trousers descended and appeared on top of brown loafers through the little gap under the cubicle wall. The heavy-set man dumped himself onto the john and exhaled.
After he deleted the message, Fabian switched off the phone and wiped the power back into his remote charger. He scrubbed his prints off the brick and replaced it behind the bowl. Another flush and he was gone. Out the door before charcoal trousers could physically tie him to the brick. If he was snooping, they would know. He’d get questions about using an unsanctioned jailbroken device. Maybe he could claim he was trying to arrange a physical meeting with T1n4Red. Still, the interrogation would be brutal.
Back on the floor, Agent Williams activated a meeting alert on Fabian’s desk. The red light informed him he must report to the cube immediately. It took great restraint for Fabian to avoid any nervous ticks. Especially with the scrutiny of operatives at his level, he couldn’t avoid a single nervous exploration of the moles on his temple or wiping of hands on trousers. The electronic band every citizen had clamped around their right wrist fed streams of bio-data to the DoS servers. Who would be alerted if his heartbeat spiked or breathing patterns changed? As he’d learned on the L2 forums, flying under the radar took a lot more than digital restraint. The surveillance apparatus of the state kept so much biometric data it had become a living cyborg. Could this be about the bathroom break? The guy in the next stall with the charcoal trousers? The brick? Was this the start of a downfall that ended in the same invisible blacklist Scott was on? Maybe that chick in the library had something against him too.
The glass door slid open and Fabian moved through the entry point in one clean step.
“No need to sit, Operative Sixsmith. Let’s stay on our feet here.”
Sixsmith awaited the news. Whatever it was, at least it would be quick.
Williams raised a stainless steel travel mug to his lips and drank. If the coffee was hot, he showed no signs of it. “I must admit, I’ve had my doubts about you.” An ominous start. “Up until this year, your work was adequate.” Williams paced towards the glass wall to watch the goings on of the morning-shift operators. His invisible stare could put someone’s back out. “And that stunt you pulled to get the jump on T1n4Red… some stricter agents might have filed that as a denial-of-protocol infraction.”
Fabian locked his gaze to the coffee cup and let him talk.
“But since then, your results have been quite something. An 89% strike rate on intel and twelve L2 agitators liquidated. That’s as high as I’ve seen.”
“Thank you, sir.” Fabian rearranged his cotton shirt, which, despite the blasting air con, was stuck firmly to his back.
“Good news.” Agent Williams went to his desk drawer and removed a six-inch blade. The silver tip matched the glint of William’s graying hair under the strip light. “You are no longer an operative here at the Department of Surveillance.”
Fabian imagined the angle of attack. A diagonal slashing motion from up high. He wouldn’t have time to avoid the agent’s quick reflexes.
“Congratulations, Agent Sixsmith.”
Fabian took a step back. His right hand found its way to his brow. “What?”
“You’ve been promoted, son. It can’t be that much of a surprise.”
Fabian had spent so long tracking certainties, he had forgotten what surprise felt like. He had his doubts about the system, his L3 secrets, his upcoming liaison with T1n4Red, his friendship with Scott. But things would be better as an agent. His family back in Boston would surely offer some begrudging respect. If he wasn’t six feet under, his old man might feel some kind of peace knowing his boy had won back those credits. Freedom from bio-data collection and freedom to roam. He faced his boss. “But I’m not up for review until—”
“Take the win.” Williams approached, knife in hand. “We need all the capable agents we can get.” He reached for Fabian’s right forearm. His grip was that of a much bigger man. “Effective immediately, you are Agent Sixsmith of the Department of Surveillance.” He slid the knife under Fabian’s communicator wristband and sliced through the strap.
The cool office air touched his now naked wrist. Fabian smoothed the skin as if he had been unshackled.
Once Williams returned the knife to its drawer, he offered his hand to shake. “Congratulations, Agent. Full briefing tomorrow at 0930.”
“Yes sir. Thank you for your trust.” He turned to go.
“Stop,” a sharp voice called. Williams held a small piece of metal between thumb and forefinger. “Don’t forget this.”
Agent Fabian Sixsmith accepted the gift — an American flag pin. He nodded and stepped through the doorway in the same way he entered.
](https://image.nostr.build/b3cff409a4d05409b84ddd61f9689f707b24376f196887558c2eaee1d17c8275.jpg)
Fabian zipped his thick hoodie and stepped out into the night. The reflectors in the fabric would dazzle the night vision of the cameras, and the Federal Government hadn’t passed any laws telling people how to dress… yet. He opened the door and set out to meet his handler.
He started his run towards the city outskirts, the hood shrouding his adrenaline-shot eyes. The back of his skull throbbed. It had been bothering him all afternoon. Throwing in a few boxing moves for good measure, Fabian pounded out the miles. One, two, past the city limits and onto the shoulder of the 87, the sixteen-wheeler auto rigs ripping past. The drones would be following — of that he was sure.
His handler was there. Just like Tina said. Half a mile after the first junction, under the bridge, Scott straddled his solarbike. This must be how he earned his sats — acting as a go between for Underworld agents who had gone to ground.
No words, just the exchange. Fabian unzipped the hoodie and draped it over his friend’s shoulders. Scott removed a 3D image scanner from his pocket and ran it over Fabian’s face. Two seconds and the ID confirmation would be relayed on the Ledger, probably embedded with a stego message. A quick clap of the hands, and he drove into the night. Forty, fifty, sixty, and gone, west towards Great Falls. Fabian took a breath. Is this what he had done all those reps in the closet for? He scrambled up the bank and jumped for the bridge railing. Hauling his body up and over in one swift motion. Then, crouching low behind the advertising hoarding, he duck-walked over the bridge and down the bank. How would he disable the micro cameras? Even without tracking data, the DoS apparatus wouldn’t be far behind — especially after they scrambled a drone to intercept Scott. Thirty seconds tops.
This place, just a few miles away from Lewistown, was the setting for one of those books he loved — cowboys, sheriffs, and theft. Of course, the subterfuge of Level 3 protocol and 256-bit encryption was a little more complicated now. The idea of coding messages is as old as civilization, only the attack vectors changed over time.
Left. Right. Feet smacking dirt. Fabian had to trust the track was level. He could barely see three feet in front of him — only the dim Montana moonlight for company. The whirr of a camcopter approached overhead. If it locked his thermal image, he was toast. Just a few more strides surely. His lungs burned after all those miles.
DoS wasn’t just going to let a newly-minted agent go for a mysterious wilderness night run.
His foot jammed against a root. He stumbled on, narrowly avoiding a painful fall.
“IDENTIFY ORDER.” The camcopter had locked the human gait recognition. “FAILURE TO COMPLY EVOKES FEDERAL CREDIT ELIMINATION.”
Fabian almost laughed. These fucking things threatening to zero-out people’s hard-earned savings. How the hell had Americans let things go this far? He spotted the manhole cover under the tree. His lungs sucked in the night air, and his heart tore at his ribs.
Wham. Down to the ground. The force of a truck pinned Fabian and pushed his face into the dirt. “No,” he cried. “Let me explain.” Searing pain pulsed through his skull from the back to the front. In the seconds that followed, it was as if his brain was rebooting. Who was this? What were they doing?
“Neural tracer deactivated,” said the voice of the brute on top of him.
Fabian managed to turn his head. He caught a glimpse of the man, but it was too dark to see his face. The pressure on Fabian’s back slowly released. He shook the cobwebs out of his head.
As Fabian stood, he saw the guard moving away, pointing his EMP caster at the sky, sweeping left then right.
Crash. One dronecopter downed. A crash to the right, another drone gone. These things would be disposed of in some pit or quarry. The figure collected the drones and moved into the night.
Fabian dusted himself off and walked towards his destination of the irrigation pipe system. As Agent Sixsmith hauled the steel grate to the side, he took a breath. This was it. Too late to deny involvement. Too far down the rabbit hole. He’d have to give up everything he worked for — respect at Thanksgiving and a pension large enough to retire to a ranch and ride a horse over the land. In exchange, he’d get a one-time Underworld trip, where he would learn the methods and tactics the punks used to stay off grid.
Now it was quiet, bar the low hum of the highway and the sound of his rasping breath. He’d never been this alive. It sure beat the meticulous protocol of DoS. Before he could stop himself, Fabian was inside, his hands replacing the grate, gripping the ladder, his feet on the rungs, stepping down, down into the dark. Whatever she had to tell him, he needed to hear it. Meeting T1n4Red in the meatspace trumped any handshake from Agent Williams, any pension plan, and any begrudging respect from his nagging mother and fucked-up family. He descended to the Underworld.
At the end of the dank tunnel, Fabian saw the purple glow of UV light. He approached slowly. The sound of soft footsteps approached from behind. He didn’t dare turn. Then, a few paces from the curve where the light grew stronger, a flat plastic object jammed the base of his skull forward. Click. Probably a 3D-printed gun.
“Arms out. Legs astride.”
Fabian complied. The EM scan wouldn’t find anything. He was stripped of all tech — one of the many firsts he’d experienced that day. It was safer for all parties if he didn’t turn around.
The voice barked, “Clear,” and a rough hand pushed him forward. The footsteps descended back towards the tunnel opening.
Peering into the mirror positioned at the tunnel corner, Fabian caught a glimpse of the woman he came to see. The channel between well-defined back muscles drew his eye south. How long had it been since he felt the touch of a woman? How did she stay in such good shape down here? The weak UV light faded to a soft yellow glow in the chamber.
“Agent Sixsmith. We’ve been expecting you.” Tina pulled a t-shirt over her bra and cinched her blonde hair into a top bun. She laughed. “Take a seat.”
“How do you know I’m an agent?” Fabian sat on the plastic chair closest to him. The room had been widened from its original layout. It was now around fifteen feet square with a camp bed, a desk with double monitors, and a treadmill. His eyes settled on the black desktop compu-box.
She touched his arm, her hand surprisingly warm. “I bet you’d love to open that up and take a look.”
Fabian had never seen a homemade device connected up. Getting the parts must have taken years, but nobody could detect unregistered tech through lead linings and all the perimeter protocal. She truly owned something, even if it was just a little black box.
“You didn’t think agents are unsurveilled, did you? Poor boy.”
Fabian’s mind switched to rational mode. Was he burned? Would he ever be able to surface without getting financially or physically liquidated?
“Relax. I know what you’re thinking. This is your first trip here, but it won’t be your last. We fried your tracer chip and they can’t admit they implanted ‘cause it ain’t legal.” She swiveled the computer chair and sat on it back to front. The high chair back almost came up to her chin. “You get one question. Shoot.”
In their digital conversation, Tina had always been careful to give instructions only, never responding to Fabian’s questions. He might have a lot to learn, but at least he wasn’t living in the dark like her, a trapped soldier unable to look above the parapet. Was he walking into a trap? Was he already in one? If things got tough in the interrogation he was sure to receive from Williams, he could always offer some Underworld secret. Fabian turned to face the shadow of a woman he had chased for nearly a year. “Where are the Level 3 relay servers kept?”
“Ooh amor, you’ve gotta think bigger than that.” Tina Red was more than just a celebrity crush. Her blue eyes burned with the intensity of a neutron star. Her slender legs wrapped around the chair like a boa constrictor drawing in its prey. She drew closer, and he could smell the sweat. “There are no dedicated L3 relay servers. We’ve been using a hacked DoS server for months. Keeps you searching for that mythical Underworld data center, right?”
There were so many units in the DoS server cities that it would take years to isolate the hack. Smart. “What’s the end goal to all of this?” he asked.
Instead of replying, Tina shook her head.
Play by Underworld rules, Fabian. It didn’t matter — he knew. Reversing the grip of the big-government machine was virtually impossible, but the dream was that the country returned to ‘the land of the free.’ Freedom to secrecy. Freedom to own. Freedom to transact with whomever you wanted.
Fabian watched as T1n4Red stood and crossed the six-foot gap between them. She leant over and moved a hand to the back of his hair, gripping his short black hair in her fist. The same fear pulsed through him as in the meeting he’d had with Agent Williams — the same Williams who was organizing the search and interrogate protocol for him at that very moment. Was her bodyguard waiting around the corner with the 3D-printed gun, primed to deliver its one shot straight into his brain?
“This is our endgame.” Their faces were inches apart. He saw the same freckles and imperfections in her skin as in the high-res digital render. But there was nothing like real life.
And then, a swell of the tide inside him. Euphoria. The kiss was deep. Their lips fused, one person, one dream. Fabian’s hands reached for the shape of the woman he’d dreamed about so many nights. She sat, straddling his legs and they went on. Blood rising like an ocean swell, Fabian dived into bliss. It all melted away — the dronecopters hovering above, the awkward entry to the office tomorrow, the nagging fear that his accounts would be zeroed out in mere hours. But one image remained. The moment transported Fabian to his spiritual home — the wilds of the Montana hills, the wind blowing through the grassland, the mountain range guarding the horizon. The wild country that called him.
When they finally broke the kiss, Tina stood. “Did you feel it?”
Fabian raised his gaze. “I think so. A place. The wild—”
She raised a finger to silence him. “Don’t say it. This is our secret, Agent Sixsmith.”
He thought for a second. Project Wild Country. It was strange, but he had no doubt. The phrase was branded into his mind clearer than the passphrase he had to memorize for his DoS access. How could two beings communicate telepathically?
“It’s called ‘Telepathic Key Exchange’. TKX for short.” Tina approached and whispered into his ear. “From the mentalists of the late 20th Century.” It had been there all along — a method to eliminate the gap where biological beings had to enter a passphrase physically. This was only part of the information chain without a cipher. No more worries about the micro cameras that could capture keystrokes or capture pen and ink comms.
“Our project,” she breathed.
The image swam through Fabian’s mind once more, the color of the sky as vivid as the eyes of the woman in front of him. The hills and plains in front of them. All protests start with the spark of non-compliance. And all revolution hinges on the man who knows how to play both sides. He’d have to learn more about it, understand it better, but TKX could lay the path to a fully anonymous market, unbreakable smart contracts, and a citizens’ private arbitration court. This would be the rewilding of America.
“We only have a few more minutes.” Tina returned to her chair. She explained the comms protocol and that the two of them were the only people on Earth to know the name of this mission. Project Wild Country would bring TKX to the masses.
“How can we teach people?”
“We lead people through the levels, just like I got you here. There are more stego images on the Ledger every day. It’s already started.”
Fabian looked at the wrist his bio-band had once gripped. “What do I say to DoS to explain this time-gap?” How long had he even been down there, fifteen minutes?
“You wouldn’t be much of an agent if you couldn’t think of something. Be the sovereign of yourself, Fabian.” T1n4Red laughed. “Better get running.”
Fabian moved toward the dark tunnel that led to a surface world buzzing with invisible spies. “I’ll be thinking of you,” he said. Fabian thought he detected the hint of a smile on Tina’s lips, and he felt a tiny swell of the euphoria that had filled him moments earlier. Then, he turned to go. Agent Sixsmith rounded the corner and started his journey back to the wild country.
This story first appeared in Financial Fallout. Find out more about the book at 21futures.com
21 Futures retains 21% of the zaps received to cover operating costs. The majority of the sats are forwarded to the author.
Max Hillebrand is a praxeologist who contributes to several open-source projects, because code is abundant and not scarce. He shares his work freely for others to use and modify. His goal is to help build a parallel economy based on sound money and individual sovereignty, where people can pursue their entrepreneurial ambitions without interference from central authorities. Find out more at towardsliberty.com
-
 @ e4950c93:1b99eccd
2025-05-02 09:41:12
@ e4950c93:1b99eccd
2025-05-02 09:41:12Tu connais une marque proposant des alternatives naturelles ? Partage-la ici en commentant cette page !
Pour être référencée, la marque doit proposer une partie au moins de ses produits en matières naturelles. 👉 En savoir plus sur les matières
Chaque information ajoutée (nom, lien, catégorie, etc.) et validée est considérée comme une contribution. 👉 En savoir plus sur les contributions
Chaque contribution validée est comptabilisée et donne lieu à une rétribution. Pense à bien sauvegarder tes clés (identifiants) dans un coffre comme nsec.app). Tu peux aussi partager plus simplement tes trouvailles sans créer de compte via le formulaire de contact (non éligible pour les rétributions). 👉 En savoir plus sur les rétributions
Copie-colle le modèle ci-dessous et remplis les informations que tu as. D’autres contribut-eur-rice-s ou l'équipe coeur pourront compléter les éléments manquants.
Nouvelle marque ou fabricant
- Nom de la marque :
- Image représentant des produits de la marque (lien, idéalement depuis le site de la marque) :
- Courte description :
- Catégories de produits proposées :
- Matières utilisées pour ses produits :
- Site internet de la marque :
- Autres informations (lieu de production, labels…) :
Cet article est publié sur origine-nature.com 🌐 See this article in English
-
 @ a5142938:0ef19da3
2025-05-02 09:39:05
@ a5142938:0ef19da3
2025-05-02 09:39:05Do you know a brand offering natural alternatives? Share it here by commenting on this page!
To be listed, the brand must offer at least some of its products made from natural materials. 👉 Learn more about materials
Each piece of information added (name, link, category, etc.) and validated is considered a contribution. 👉 Learn more about contributions
Every validated contribution is counted and eligible for rewards. Make sure to securely save your keys (credentials) in a vault like nsec.app). You can also share more easily your finds without creating an account via the contact form (not eligible for rewards). 👉 Learn more about rewards
Copy and paste the template below and fill in the information you have. Other contributors or the core team can complete any missing details.
New brand or manufacturer
- Brand name:
- Image representing the brand’s products (link, ideally from the brand’s website):
- Short description:
- Categories of products offered:
- Materials used in its products:
- Brand’s website:
- Other information (place of production, certifications, etc.):
This article is published on origin-nature.com 🌐 Voir cet article en français
-
 @ ca495706:2476e4d0
2025-05-02 09:38:12
@ ca495706:2476e4d0
2025-05-02 09:38:12VIPWIN là một nền tảng trực tuyến phát triển mạnh mẽ trong thời gian gần đây, mang đến cho người dùng những trải nghiệm mượt mà và an toàn. Được thiết kế với giao diện thân thiện và dễ sử dụng, VIPWIN không chỉ chú trọng đến việc tối ưu hóa trải nghiệm người dùng mà còn bảo vệ quyền lợi của họ một cách tối đa. Tính năng của nền tảng này luôn được cập nhật và cải tiến để phục vụ nhu cầu ngày càng cao của người dùng. VIPWIN cung cấp một không gian trực tuyến hiện đại, dễ tiếp cận, cho phép người dùng truy cập các dịch vụ chỉ trong vài bước đơn giản. Dù bạn là người mới sử dụng hay là người đã có kinh nghiệm, việc làm quen với hệ thống của VIPWIN sẽ rất dễ dàng nhờ vào giao diện trực quan và các tính năng hỗ trợ rõ ràng. Một trong những yếu tố quan trọng tạo nên sự khác biệt của VIPWIN chính là tốc độ truy cập ổn định và nhanh chóng. Người dùng sẽ không gặp phải tình trạng gián đoạn hay độ trễ trong suốt quá trình sử dụng dịch vụ.
Bảo mật là một trong những yếu tố quan trọng mà VIPWIN đặc biệt chú trọng. Với sự phát triển không ngừng của công nghệ, việc bảo vệ thông tin cá nhân của người dùng là vô cùng cần thiết. VIPWIN sử dụng các công nghệ mã hóa tiên tiến để đảm bảo rằng dữ liệu của người sử dụng luôn được bảo vệ an toàn tuyệt đối. Các thông tin giao dịch và dữ liệu cá nhân đều được mã hóa, giúp người dùng yên tâm khi sử dụng nền tảng mà không phải lo lắng về việc bị lộ lọt thông tin. Ngoài ra, đội ngũ bảo mật của VIPWIN luôn theo dõi và kiểm tra hệ thống thường xuyên để phát hiện và xử lý kịp thời các mối đe dọa tiềm ẩn. Điều này giúp người dùng hoàn toàn tin tưởng vào sự an toàn của nền tảng. Không chỉ vậy, VIPWIN còn cung cấp dịch vụ hỗ trợ khách hàng chuyên nghiệp, hoạt động liên tục 24/7, sẵn sàng giải đáp mọi thắc mắc và hỗ trợ người dùng khi gặp phải vấn đề. Đội ngũ hỗ trợ của VIPWIN luôn tận tâm và chu đáo, đảm bảo người dùng luôn được hỗ trợ nhanh chóng và hiệu quả.
Với cam kết phát triển không ngừng và cải tiến liên tục, VIPWIN không chỉ đáp ứng nhu cầu của người dùng mà còn luôn tạo ra những giá trị mới cho cộng đồng. Nền tảng này luôn cập nhật và cải tiến các tính năng để mang đến cho người dùng những trải nghiệm tối ưu nhất. Các tính năng mới luôn được phát triển dựa trên nhu cầu thực tế của người sử dụng, nhằm cải thiện hiệu suất và nâng cao chất lượng dịch vụ. VIPWIN luôn chú trọng đến việc cải tiến giao diện, nâng cao tốc độ truy cập và cập nhật các công cụ hỗ trợ người dùng. Một điểm đáng chú ý nữa là nền tảng này luôn sẵn sàng lắng nghe ý kiến đóng góp từ cộng đồng người dùng, từ đó đưa ra các thay đổi và cải tiến phù hợp. Chính nhờ sự sáng tạo và cam kết không ngừng nâng cao chất lượng dịch vụ, VIPWIN đang ngày càng trở thành lựa chọn hàng đầu của người dùng trong môi trường trực tuyến. Với đội ngũ phát triển chuyên nghiệp và tầm nhìn dài hạn, VIPWIN chắc chắn sẽ tiếp tục phát triển mạnh mẽ và duy trì vị thế là một trong những nền tảng trực tuyến đáng tin cậy nhất trong tương lai.
-
 @ a5142938:0ef19da3
2025-05-02 09:37:56
@ a5142938:0ef19da3
2025-05-02 09:37:56Have you found a natural product? Share it here by commenting on this page!
This site only lists durable-use products and objects. Consumables (food, cosmetics, fuels, etc.) are not included.
To be listed, the product must be made of natural materials. 👉 Learn more about materials
Each piece of information added (name, material, link, shipping area, etc.) and validated is considered a contribution. 👉 Learn more about contributions
Every validated contribution is counted and eligible for rewards. Make sure to securely save your keys (credentials) in a vault like nsec.app). You can also share more easily your finds without creating an account via the contact form (not eligible for rewards). 👉 Learn more about rewards
You can copy and paste the template below and fill in the information you have. Other contributors or the core team can complete any missing details.
New product
- Product name :
- Product image (link):
- Short description:
- Categories:
- Brand or manufacturer:
- Composition (materials used, including unknown elements):
- Links to buy (and shipping area):
- Other information (place of manufacture, certifications…):
This article is published on origin-nature.com 🌐 Voir cet article en français
-
 @ e4950c93:1b99eccd
2025-05-02 09:36:09
@ e4950c93:1b99eccd
2025-05-02 09:36:09Tu as trouvé un produit naturel ? Partage-le ici en commentant cette page !
Ce site référence uniquement des produits et objets à usage durable. Les consommables (aliments, cosmétiques, combustibles, etc.) ne sont pas inclus.
Pour être référencé, le produit doit être composé de matières naturelles. 👉 En savoir plus sur les matières
Chaque information ajoutée (nom, matière, lien, zone de livraison pour un lien, etc.) et validée est considérée comme une contribution. 👉 En savoir plus sur les contributions
Chaque contribution validée est comptabilisée et donne lieu à une rétribution. Pense à bien sauvegarder tes clés (identifiants) dans un coffre comme nsec.app). Tu peux aussi partager plus simplement tes trouvailles sans créer de compte via le formulaire de contact (non éligible pour les rétributions). 👉 En savoir plus sur les rétributions
Copie-colle le modèle ci-dessous et remplis les informations dont tu disposes. D’autres contribut-eur-rice-s ou l'équipe coeur pourront compléter les éléments manquants.
Nouveau produit
- Nom du produit :
- Image du produit (lien) :
- Description courte :
- Catégories :
- Marque ou fabricant :
- Composition (matériaux utilisés, y compris les éléments inconnus) :
- Liens pour l’acheter (et zone de livraison) :
- Zone de livraison pour les
- Autres infos utiles (lieu de fabrication, labels, etc.) :
Cet article est publié sur origine-nature.com 🌐 See this article in English
-
 @ fbb0eb9d:bdb78256
2025-05-02 09:32:40
@ fbb0eb9d:bdb78256
2025-05-02 09:32:40Wir dürfen keinen Millimeter weichen für jene, die unsere Freiheit nicht zu schätzen wissen. Vor zehn Jahren wurden die Journalisten des französischen Satiremagazins Charlie Hebdo in ihrer Redaktion erschossen, weil sie sich die Freiheit nahmen, eine Religion zu beleidigen. Das sollten wir nicht vergessen, und beim Namen nennen. Diesen Text schrieb ich schon damals, und um es vorweg zu nehmen: Ich bin immer noch Charlie.
„Und, sind Sie auch Charlie?“ fragte damals mein Banksachbearbeiter, nachdem ich auf die Frage nach meinem Beruf „Journalistin“ geantwortet hatte. Viele waren seinerzeit „Charlie“, ja, die Solidarität mit den Opfern in Paris war groß. Bei uns im Land und auch weltweit. Tausende Facebooker veränderten ihre Profilbilder, aber genauso sicher, wie das Amen in der Kirche, hatte es nur wenige Tage gedauert, bis die Differenzierer auf den Plan gerufen wurden. Am Tag der Geiselnahmen in Paris fuhr ich gerade Taxi in Berlin, während sich die französischen Sondereinheiten vor der Druckerei und dem jüdischen Supermarkt in Stellung brachten, die ebenfalls unter Beschuss von Islamisten gerieten. Der Taxifahrer war kein potenzieller „Charlie“. Ich konnte seine Nationalität trotz Akzent nicht ausmachen, möglicherweise war er sogar Franzose. Ich habe nicht gefragt. Sein Standpunkt jedenfalls: „Warum mussten die das auch veröffentlichen, das hätte man ja wissen können, das sowas passiert“.
Wenn mehr auf dem Spiel steht, als ein Profilbild
Ein Moslem? Ich weiß es nicht. Aber auch aus dem christlichen Lager kam zunehmend Kritik, nachdem so mancher recherchiert hatte, was für Karikaturen bei „Charlie Hebdo“ in der Vergangenheit erschienen sind. Auch mit uns Christen ging man in dem Satire-Magazin nicht gerade zimperlich um. Sind wir immer noch Charlie, auch dann, wenn unsere eigene Religion aufs Korn genommen oder gar beleidigt wird?
Und so bestätigte ich dem Angestellten am Bankschalter auch gerne: „Ja, ich bin Charlie, aber ich bin auch gespannt, wie viele immer noch Charlie sind, wenn es um ihren eigenen Kopf geht!“ – eine Frage die heute kaum aktueller sein könnte angesichts von katholischen Priestern, die zwischenzeitlich im Namen Allahs in Frankreich am Altar geköpft wurden und auch islamischen Attentätern, die gerne deutsche Weihnachtsmärkte für ein adventliches Töten zum Anlass nehmen. Sind wir immer noch “Charlie” wenn die Frage nach der Solidarität mit den Opfern sich nicht mit einem Wechsel des Profilbildes bei Facebook erledigen lässt? Denn ein Bild zu tauschen, tut nicht weh, ist schnell gemacht und man bewegt sich damit gerade sowieso im Strom der breiten Masse.
Gesicht zu zeigen ist ein Anfang, es bis zur letzten Konsequenz durchzuhalten, oft etwas ganz anderes. Auch Prominente zeigten damals vor zehn Jahren gerne immer wieder Gesicht. Es existierte eine ganze Kampagne dazu unter dem Namen.
Da war dann Klaus Wowereit Migrant, wenn jemand was gegen Migranten hat, Jörg Thadeusz war schwul, wenn jemand etwas gegen Schwule hat, Ulrich Wickert war Jude, wenn jemand etwas gegen Juden hat und Markus Kavka gar schwarz, wenn jemand was gegen Schwarze hat.
 Das ist auch gut so, so wird Flagge gezeigt. Aber es braucht für derlei Bekenntnisse genauso wenig Mut, wie für den Profilbild-Wechsel bei Facebook.
Das ist auch gut so, so wird Flagge gezeigt. Aber es braucht für derlei Bekenntnisse genauso wenig Mut, wie für den Profilbild-Wechsel bei Facebook.Denn sind wir wirklich immer noch „schwarz“, „schwul“, „Jude“ oder „Migrant“, wenn unser Nebenmann angegriffen wird? Kurz nach der Ermordung der Satiriker von Charlie Hebdo bekam damals Ralf König auf Facebook und Co. von allen Seiten die Comiczeichner-Jacke vollgehauen, weil er nicht mehr ganz Charlie sein mag. Aus Angst hatte er eine Karikatur zurückgezogen, die sich mit dem Islam beschäftigte. Bei ihm steht ja auch nicht nur ein Profilbild, sondern – wie Paris gezeigt hat – wesentlich mehr auf dem Spiel. Eine allzu menschliche Reaktion! Und all den Heuchlern, die ihn verurteilen, würde ich gerne zurufen: Euch möchte ich mal in der gleichen Situation erleben. Nämlich dann, wenn es persönlich wird und die Angst nicht abstrakt, sondern konkret begründet werden kann.
Gerade Christen dürfen nicht zurückweichen
Das zeigt aber gleichzeitig, warum es so wichtig ist, dass wir auch weiterhin Charlie sind. Weil die Angst im Kopf uns sonst lähmt.
Wenn ein Journalist anfängt nachzudenken, ob er überhaupt oder wenn, wie er etwas schreiben soll, dann hat die Selbstzensur bereits eingesetzt.
Wenn ein Journalist Fakten weglässt, weil er vermutet, dass sie nicht gerne gehört werden, dann hat Selbstzensur schon eingesetzt.
Wenn ein Zeichner sich nicht mehr traut, manche Themen oder Religionen aufs Korn zu nehmen, dann hat Selbstzensur schon eingesetzt.
Und dann nutzt es nichts, dass gesetzlich keine Zensur existiert, weil diese Gesetze dann nicht mehr das Papier wert sind, auf dem sie stehen. Wir dürfen nicht zurückweichen. Auch und gerade nicht als Christen. Auch wenn wir selbst mit manchen Karikaturen hadern. Beleidigt sein darf man trotzdem. Denn der Grad von persönlicher Entrüstung ist bei allen unterschiedlich. Ich jedenfalls habe Tränen gelacht beim Kinoklassiker „Life of Brian“ und Monty Pythons „Catholic Song“ ist einfach ganz großes Kino. Aber auch ich war schon oft empört, weil mir manches, was unter Satire und Kunst verkauft wird, zu weit ging.
„Würden Sie auch Mohammed-Town ausstrahlen?“
Als etwa 2003 der Musiksender MTV die Comic-Serie „Popetown“ mit einem infantilen Papst und korrupten Kardinälen ausstrahlte, habe ich eine Gegenkampagne dazu organisiert. „Würden Sie auch Mohammed-Town“ ausstrahlen, fragte ich damals in einem offenen Brief die MTV-Geschäftsführerin Catherine Mühlemann. „Kein Christ wird Ihnen bei Ausstrahlung die Studiofenster zertrümmern, handelt es sich doch beim Christentum um eine Religion des Friedens. Wir verdienen aber nicht weniger Respekt als andere Religionen.“ 50.000 Menschen beteiligten sich damals an den Protesten, verschiedene Organisationen, Politiker und sogar der Zentralrat der Juden protestierte, genutzt hat es nichts. Die Serie erledigte sich letztendlich selbst mit niedrigen Einschaltquoten dank ihres unterirdischen Niveaus.

Aber selbst, wenn es ein Erfolg geworden wäre, hätten wir weiter protestiert: friedlich und ganz sicher nicht mit dem Maschinengewehr. Wir sind ein Land, in dem diese Debatten immer und immer wieder neu mit Worten und nicht mit Waffen ausgetragen werden. In unserem Land darf man kritisieren und sich auch empören. Wir dürfen unsere eigene Regierung anprangern und uns über Religionen lustig machen. Das tut weh, wenn man selbst betroffen ist, dieses Recht dürfen wir aber nicht riskieren. Für keinen persönlichen Grad an Beleidigtsein.
Diskurs statt Blasphemie-Gesetze
Wenn wir also Rücksicht nehmen auf Religionen, dann aber bitte auf alle. Wenn Religionen aber Kritik, Humor oder Satire aushalten müssen, dann bitte auch alle. Ich halte nichts von Blasphemie-Gesetzen, aber umso mehr vom freien Diskurs, der nicht nur in der Religionsfrage derzeit ins Hintertreffen gerät.
Die Frage, ob „der Islam“ zu Deutschland gehört, ist also die falsche. Die Frage ist: Will der Islam zu Deutschland oder gar zu Europa gehören? Sind alle seine Gläubigen bereit, friedlich hinzunehmen, dass im Namen von Meinungsfreiheit, Kunst oder Satire der eigene Glaube beleidigt werden darf?
Denn erst dann ist der Islam wirklich im freien Europa angekommen und diese Frage können die Muslime nur unter sich ausmachen. Es ist nicht an uns, ihnen ihre Religion zu erklären. Wir sollten aber langsam klären, wofür wir selbst stehen. Integration kann nur von jemandem erwartet werden, dem man auch erklären kann, in was er sich integrieren und wie weit das reichen soll.
Wir werden den gemeinsamen Nenner aufzeigen müssen, die „Conditio-sine-qua-non“, ohne die sich unsere Gesellschaft sonst immer weiter auseinander bewegt. Ich habe damals von Catherine Mühlemann keine Antwort auf meine Frage bekommen. Ich weiß nicht, ob sie heute Charlie ist. Ich wünsche mir keinen Raum für diese Angst, die uns lähmt, Debatten ehrlich zu führen. Für Menschen, die unsere Freiheit nicht zu schätzen wissen, weiche ich keinen Millimeter. Ich bin Birgit Kelle. Und ich bin immer noch Charlie.
-
 @ 8f69ac99:4f92f5fd
2025-05-02 09:29:41
@ 8f69ac99:4f92f5fd
2025-05-02 09:29:41À medida que Portugal se aproxima das eleições legislativas de 2025, a 18 de Maio, torna-se essencial compreender as diferentes propostas políticas e os programas eleitorais dos partidos para votar de forma informada. Este artigo funciona como um índice para uma série de análises realizadas aos programas dos principais partidos, com foco em temas como liberdades individuais, descentralização e crescimento económico.
A Evolução da Esquerda e da Direita: Um Contexto Histórico e Ideológico
Os termos “esquerda” e “direita” surgiram na Revolução Francesa (1789–1799) para distinguir quem se sentava ao lado do presidente da Assembleia: as forças favoráveis às reformas radicais (à esquerda) e as defensoras da monarquia e da ordem estabelecida (à direita). Com o século XIX e o advento do liberalismo económico, a direita passou a associar-se ao livre mercado e ao direito de propriedade, enquanto a esquerda defendeu maior intervenção estatal para promover igualdade.
No final do século XIX e início do século XX, surgiram o socialismo e o comunismo como correntes mais radicais da esquerda, propondo a abolição da propriedade privada dos meios de produção (comunismo) ou sistemas mistos com forte regulação e redistribuição (socialismo). A resposta liberal-conservadora evoluiu para o capitalismo democrático, que combina mercado livre com alguns mecanismos de assistência social.
Hoje, o espectro político vai além do simples eixo esquerda–direita, incluindo dimensões como:
- Autoritarismo vs. Liberdade: grau de controlo do Estado sobre a vida individual e as instituições;
- Intervenção Estatal vs. Livre Mercado: equilíbrio entre regulação económica e iniciativas privadas;
- Igualdade Social vs. Mérito e Responsabilidade Individual: ênfase na redistribuição de recursos ou na criação de incentivos pessoais.
Este modelo multidimensional ajuda a capturar melhor as posições dos partidos contemporâneos e as suas promessas de governação.
Visão Geral das Análises por Partido
Segue-se um resumo dos principais partidos políticos em Portugal, com destaque para a sua orientação ideológica segundo as dimensões de autoritarismo, nível de Intervenção estatal e grau de liberdade individual. Cada nome de partido estará ligado à respectiva análise detalhada.
| Partido | Orientação Ideológica | Nível de Intervenção Estatal | Grau de Liberdade Individual | |----------------------------------------|---------------------------------------------------------------------------------------|------------------------------|------------------------------| | AD – Aliança Democrática (PSD/CDS) | Centro-direita democrática (baixo autoritarismo / equilíbrio intervenção–mercado) | Médio | Médio | | PS – Partido Socialista | Centro-esquerda social-democrata (moderado autoritarismo / intervenção estatal) | Alto | Médio | | CDU – Coligação Democrática Unitária (PCP/PEV) | Esquerda comunista/eco-marxista (mais autoritário / forte intervenção) | Muito alto | Baixo | | IL – Iniciativa Liberal | Liberalismo clássico (muito baixa intervenção / alta liberdade) | Baixo | Muito alto | | Chega | Nacionalismo autoritário (controlo social elevado / mercado regulado com foco interno)| Médio | Baixo | | Livre | Esquerda progressista verde (baixa hierarquia / intervenção social) | Alto | Médio | | BE – Bloco de Esquerda | Esquerda democrática radical (moderado autoritarismo / intervenção forte) | Alto | Médio | | PAN – Pessoas-Animais-Natureza | Ambientalismo progressista (intervenção pragmática / foco em direitos e sustentabilidade) | Médio | Alto | | Ergue-te | Nacionalismo soberanista (autoritarismo elevado / intervenção seletiva com foco nacional) | Médio | Baixo | | ADN – Alternativa Democrática Nacional | Nacionalismo conservador (autoritarismo elevado / intervenção seletiva com foco nacional) | Médio | Baixo |
Análises Detalhadas dos Programas Eleitorais
Estas análises pretendem oferecer aos eleitores uma visão clara e objetiva das propostas de cada partido, facilitando decisões conscientes nas urnas. Ao focar-se nas promessas relacionadas com liberdades individuais, descentralização e crescimento económico, este conjunto de textos ajuda a compreender melhor o impacto potencial de cada escolha política.
Aliança Democrática (AD)
Partido Socialista (PS)
Coligação Democrática Unitária (CDU)
Iniciativa Liberal (IL)
Chega
Livre
Bloco de Esquerda (BE)
Pessoas,Animais e Natureza (PAN)
Alternativa Democrática Nacional (ADN)
Ergue-te
Photo by Brett Kunsch on Unsplash
-
 @ fbb0eb9d:bdb78256
2025-05-02 09:28:33
@ fbb0eb9d:bdb78256
2025-05-02 09:28:33„Das Schlachten hat begonnen“ war im Jahr 2013 der Titel eines höchst umstrittenen – also wahrscheinlich recht realistischen – Meinungsbeitrags des Autors Akif Pirinçci. Heute ruft die Terrororganisation Islamischer Staat (IS) ganz offiziell in Deutschland genau zu jenem Schlachten auf, das der Autor damals bereits als sichtbares Schema eines außer Kontrolle geratenen Islams in Deutschland beklagte. Der Beitrag ist heute im Internet gelöscht. 12 Jahre später fordern islamische Terroristen ihre Glaubensbrüder in Deutschland auf: „Auf zum Schlachten. Worauf wartest du? Die Straßen sind voller Ziele! Überfahre sie!!“ und verbreiten dazu Bilder, bei denen der Fahrer eines Wagens die Menschen vor ihm auf der Straße ins Fadenkreuz nimmt.

Der Deutsch-Türke Pirinçci war den meisten Lesern bis zu diesem Zeitpunkt eher als weltweiter Bestsellerautor von „Felidae“ und als Erfinder der Romangattung “Katzenkrimi“ bekannt denn als politischer Autor und Kritiker des Zeitgeschehens. Sein Hang zur unflätigen und vulgären Ausdrucksweise und seine anschließenden Auftritte u. a. bei den islamkritischen „Pegida“-Demonstrationen hatten es seinen Kritikern einst leicht gemacht, den brisanten Inhalt seiner Texte und Thesen gleich mit vom Tisch zu wischen und ihn nach allen Regeln jener Kunst, die man heute als „Cancel Culture“ bezeichnet, als ihr erstes prominentes Opfer ins komplette Abseits zu katapultieren. Nun schreibe ich das nicht, um zur späten Rehabilitierung eines Kollegen anzusetzen, sondern weil es sich lohnt, die Genese dieses Vorgangs heute zu betrachten, um sich ehrlich zu fragen: Kommen einem die medialen und politischen Reaktionen nicht doch sehr bekannt vor? Und wenn man das damals alles schon sehen konnte, warum sind wir über ein Jahrzehnt später immer noch nicht weiter?
Ein Exempel wird statuiert
Da schreibt also ein Autor bereits vor 12 Jahren, selbst als Türke mit Einwanderungsbiografie, eine scharfe Kritik an der deutschen Einwanderungspolitik, die mit den Menschen einen Islam zu uns bringt, der sich in Gewalt entlädt und die einheimische Bevölkerung bedroht. Aufhänger des Textes war 2013 der Todesfall des 25-jährigen Lackierers Daniel S., der von einem herbeitelefonierten Schlägertrupp an einer Bushaltestelle abgepasst wurde und später an seinen Kopfverletzungen verstarb. Die Täter hatten türkischen Migrationshintergrund, manche waren bereits polizeibekannt, beides verschwieg die Polizei in ihrer Pressemitteilung an die Öffentlichkeit, bis die BILD-Zeitung die ganze Wahrheit druckte.
Der später verurteilte Täter war statistisch „Deutscher“, seine Tat zahlt in die Polizeistatistik der Deutschen ein, da er in Deutschland geboren wurde, also bereits zweite Generation Einwandererkind ist, man kann seine Integration und die seiner Freunde aber als gescheitert bezeichnen. Pirinçci verliert danach alles, man streicht Verträge, er wird nicht mehr gedruckt und sein Verlag, der vorher Millionen mit ihm verdient hatte, lässt ihn hängen, weil sich gutmenschelnde Autorenkollegen des Verlages von ihm distanzieren und seinen Kopf fordern, schließlich gilt der Türke Pirinçci jetzt als Rassist und als islamophob. Die Läden nehmen seine Bücher aus den Regalen und selbst die Katzenromane aus dem Sortiment. Das Schlachten geht derweil unbehelligt weiter. Ein Kritiker weniger und dazu ein Exempel statuiert: Wagt nicht, dieses Thema anzufassen.
Blutspur durch Europa
Das Schlachten hat schon lange begonnen, nicht erst jetzt. Wie eine Blutspur ziehen sich die Tatorte und Attacken zugewanderter Migranten auf die europäische Bevölkerung seit 20 Jahren über die Landkarte. Von den inzwischen täglichen Messerattacken, die man schon gar nicht mehr mitzählt, bis zu größeren Anschlägen ist alles dabei. Die Tatwaffen ändern sich, die Orte auch, aber das Schema bleibt: Einheimische werden von islamischen Zuwanderern ermordet, absichtlich totgefahren, abgestochen, erschossen, geköpft, in die Luft gesprengt. Es geschieht in Deutschland, in Österreich, massiv in Frankreich, in Belgien, in England, Spanien und auch in Schweden.
Manche dieser Taten liegen schon sehr viele Jahre zurück, manche, die heute „gegen rechts“ auf die Straße gehen, wenn wieder einmal ein Islamist das Gedankenkonstrukt der Vielfalt gefährdet, waren damals noch in der Kita. Spätestens seit 2015 und der Terrorwelle in Frankreich ist das Thema in ganz Europa präsent. Die Journalisten des Satiremagazins Charlie Hebdo werden im Januar 2015 in ihrer Redaktion niedergemetzelt, 11 Tote. Die Botschaft: Leg dich nicht mit Mohammed und seinen humorlosen Gesellen an. Am Tag darauf ein jüdischer Supermarkt in Paris, 4 Tote und eine Geiselnahme. Dann im November 2015 koordinierte, islamistische Attentate mit insgesamt 130 Toten und 683 Verletzten zwischen Sprengsätzen am Stade de France über Zufallsopfern in Bars und Restaurants bis zu einem Blutbad mit 89 Toten, die in der Konzerthalle Bataclan mit Maschinengewehren wahllos niedergemetzelt werden.
In der darauffolgenden Silvesternacht wird Köln Schauplatz Hunderter Übergriffe von Migranten auf Frauen. Ein Auto als Waffe? Premiere schon 2016 auf dem Boulevard von Nizza mit 86 Toten und über 400 Schwerverletzten am Nationalfeiertag. In Deutschland folgt das Schema erstmals im selben Jahr im Dezember 2016 auf dem Weihnachtsmarkt am Breitscheidplatz. Im März 2016 sprengen sich in Brüssel Islamisten am Flughafen und auf einem Bahnhof in die Luft und hinterlassen 32 Todesopfer aus 22 Ländern und unzählige Verletzte. Am Jahrestag ein Jahr später rammt sich ein Islamist in London auf der Westminsterbrücke seinen Weg durch eine Menschenmenge. Spanien hatte die Terrorwelle bereits 2004 eingeholt, es kostete fast 200 Tote und fast 2.000 Verletzte, dass Islamisten koordiniert vier Züge Richtung Madrid hintereinander in die Luft sprengten. Zwei Jahrzehnte Terror in Europa. Dazwischen Machetenangriffe, geköpfte Priester, ermordete Filmemacher, ermordete Lehrer, die es wagen, das Thema in der Schule zu behandeln, Sprengsätze, vergewaltigte und ermordete Frauen und Islamkritiker, die nur noch mit ständigem Personenschutz leben können. Nur eines bleibt immer gleich: Niemand verändert die Migrationspolitik. Alle sind bemüht, stattdessen den Kampf gegen Islamophobie und Rassismus unbedingt zu verstärken, auf zur Demo gegen rechts!
Vergessene Opfer
Das Schema der medialen und politischen Verarbeitung blieb immer konstant: verschweigen, kleinreden, vergessen. Die Erinnerungskultur der Deutschen beschränkt sich gerne auf die Opfer der Nationalsozialisten und auf jene Ausländer, die von Deutschen ums Leben gebracht wurden. Hier werden, wie gerade erst vor wenigen Tagen, immer noch gerne die Namen der Opfer von Hanau von deutschen Politikern in den Medien wiederholt. Doch kennt jemand die Namen der Opfer vom Breitscheidplatz, also jenem Anschlag, der einst auslöste, dass heute jeder Weihnachtsmarkt in Deutschland zur Hochsicherheitszone aufgerüstet wird und bei dem die Politik einst peinlich bemüht war, nicht von einem islamistischen Anschlag zu sprechen? Und selbst das hat das nächste Schlachten in Magdeburg ja nicht verhindern können.
Kennt jemand die Namen aller Opfer vom Weihnachtsmarkt in Magdeburg? Kollegen bei der WELT recherchieren derzeit dankbarerweise die Folgen alleine dieses Anschlags akribisch nach. Man spricht von 1.300 Opfern insgesamt, 6 Toten, 300 Verletzten, davon 67 Schwerverletzten, einem Querschnittsgelähmten und zahlreichen Opfern, die Hände, Füße oder gar ein Bein verloren haben. Warum berührt es nicht alle gleichermaßen? Die Folgen sind keine Umkehr in der Migrationspolitik der Regierung, sondern weitere, staatlich mitorganisierte und mitfinanzierte Demonstrationen „gegen rechts“. In Aschaffenburg sind Kindergartenkinder das Opfer, ein Helfer bezahlt seinen Mut mit dem Leben, für einen Zweijährigen kommt jede Hilfe zu spät. In München fährt vor wenigen Tagen ein Islamist in eine Demonstration, eine Mutter und ihr Kind werden unter den Wagen gezogen, sie sind verstorben, noch am selben Abend demonstriert man in München „gegen rechts“, während Dutzende Schwerverletzte in den Krankenhäusern liegen und der Täter im Gefängnis reklamiert, man möge seine Zelle von der imaginären Verschmutzung durch Christen reinigen. Wenige Tage später sticht im österreichischen Villach ein Migrant wahllos in der Innenstadt Passanten nieder, ein 14-Jähriger stirbt. Der Täter lacht bei seiner Verhaftung. Die Polizei in Wien nimmt vor zwei Tagen einen 14-Jährigen fest, er plante einen Anschlag auf den Westbahnhof. Wien hatte bereits 2020 einen eigenen Amoklauf mit 4 Toten und erst im Sommer 2024 musste dort ein Taylor-Swift-Konzert wegen dringenden Terrorverdachts abgesagt werden. In Schweden wurde vor wenigen Wochen ein Islamkritiker während eines Live-Streams durch Islamisten erschossen. Europa 2025.
Man wird müde, die immer selben Worte zu wiederholen bei den sich immer enger taktenden Anschlägen von Migranten in unserem Land und in Europa. Es fehlen die Worte, weil bereits alles gesagt ist. Genauso, wie sich die sinnlosen Floskeln der Politiker wiederholen, wenn wieder eine junge Frau, ein Kind, ein Vater oder ein mutiger Helfer sein Leben lassen muss und das Volk in der verbalen Litanei erstickt wird zwischen „verwirrter Einzeltäter – Betroffenheit – wir lassen uns nicht spalten – Stadt XY bleibt bunt und wir lassen uns die Art zu leben nicht nehmen“. So, als würden nicht bereits die ersten Karnevalsumzüge abgesagt, weil die Sicherheit auf den Straßen nicht mehr garantiert werden kann.
Wir demonstrieren uns zu Tode
Was, wenn gar nicht die AfD das Problem ist, sondern der Islam? Man stelle sich für eine Sekunde vor, die AfD wäre erfolgreich bekämpft und weg. Eine Nulllinie, von der man in den Jahren 2014 und 2015 gar nicht so weit entfernt war. Damals stand die AfD in den Umfragen irgendwo zwischen 2 und 4 Prozent und tat gerade das, was nahezu alle neuen Parteigründungen der vergangenen 30 Jahre taten: Sie zerlegten sich in innerparteilichen Streitigkeiten selbst. Doch dann öffnete Angela Merkel die Grenze zur unkontrollierten Migration nach Deutschland und lieferte über Jahre ein Thema, an dem sich die AfD wie ein Phoenix aus der Asche wieder neu erhob. Denken wir also eine Sekunde, die AfD sei als Problem weg, welche Probleme sind dann immer noch da? Nichts von dem, was gerade in Deutschland relevant ist, wäre gelöst. Rezession, Wirtschaftskrise, Energiekrise, Krieg in Europa und ja, vor allem auch die gescheiterte Migrationspolitik und die Erosion der inneren Sicherheit sind dann immer noch da. Man kann natürlich die AfD exzessiv bekämpfen statt der realen Probleme, es bleibt dann aber alles, wie es ist. In einem Pseudokampf lenken die wechselnden politischen Eliten erfolgreich vom Thema ab, indem man nun bereits über ein Jahrzehnt den falschen Feind bekämpft. Gerade wird in einem Akt kollektiver kultureller Todessehnsucht das Feindbild AfD zum Feindbild CDU erweitert, um die gesamte bürgerliche Mitte von einer Umkehr in der Migrationspolitik abzuhalten. Immer noch treten brav nach jedem weiteren Anschlag wie gehirngewaschen erwachsene Menschen zu einer Demo gegen rechts an. „Wir amüsieren uns zu Tode“, resümierte einst der Autor Neil Postman die Zersetzung des Westens durch die Unterhaltungsindustrie. Deutschland hat sich im Angesicht einer kulturellen Übernahme durch zugewanderte islamische junge Männer einen weltweiten Alleingang ausgedacht: Deutschland demonstriert sich zu Tode.
Das Schlachten hat schon lange begonnen. Wer es jetzt immer noch nicht versteht, dass eine Mehrheit der illegal einreisenden Migranten weder zur Integration noch zur Arbeit und schon gar nicht wegen politischer Verfolgung hierherkommt, dem ist nicht zu helfen. Wer glaubt, er könne Millionen an aggressiven Antisemiten, glühenden Frauenhassern, Christenverächtern und Sozialstaatstouristen gesellschaftlich, kulturell und finanziell integrieren, ist realitätsfremd. An diesem Sonntag wird gewählt. Der Souverän wird seine eigene Meinung dazu kundtun, wem er zutraut, das Schlachten zu beenden.
-
 @ 1b9fc4cd:1d6d4902
2025-05-02 07:55:36
@ 1b9fc4cd:1d6d4902
2025-05-02 07:55:36To outsiders, the music industry is usually viewed as a glamorous world of fame, fortune, and creativity. However, lurking underneath the surface, the industry is also a field fraught with mental health challenges. From the history of addiction to the pressures of fame, artists have long wrestled with maintaining their mental well-being. Daniel Siegel Alonso looks at how many artists have found effective coping strategies, turning to therapy, mindfulness practices, and using music itself as a healing outlet.
The Dark History of Addiction in Music
Siegel Alonso notes that the history of addiction in the music industry is well-documented. The strain of constant touring, public scrutiny, and the never-ending pursuit of success have driven many artists to find relief in substances. Iconic musicians like Kurt Cobain, Amy Winehouse, and Jim Morrison are stark reminders of how addiction can destroy lives.
Guitarist John Frusciante of the Red Hot Chili Peppers is a notable example of someone who battled severe addiction. At the height of his career, Frusciante fell deeply into heroin addiction, which led him to leave the band in 1992. His addiction nearly cost him his life, but after a long and painful struggle, he managed to turn his life around. Frusciante’s journey to recovery involved intensive therapy and a recommitment to his music, ultimately rejoining the band and contributing to some of the group's most celebrated albums.
Seeking Help
One of the most crucial steps in addressing mental health issues is seeking professional help. Therapy provides a safe space for creative individuals to explore their thoughts, feelings, and behaviors with a trained professional. Therapy can be a lifeline for musicians, who often face unique pressures.
Frusciante’s recovery underscores the importance of professional help. He didn’t just quit drugs cold turkey; he underwent a comprehensive treatment plan that included therapy and support from friends and family. His story is a testament to the power of seeking help and the possibility of recovery, even after hitting rock bottom.
Music as an Outlet
For many musicians, creating music is more than just a career; it’s a vital outlet for expression and coping. Writing, performing, and listening to music can be powerful therapeutic tools. Music allows artists to channel their emotions into something constructive and beautiful, providing a release from their struggles.
Daniel Siegel Alonso takes The Beatles' George Harrison as an example. Harrison turned to Transcendental Meditation (TM) as a means of coping with the pressures of superstardom and personal turmoil. Introduced to TM in the 1960s, Harrison found solace and clarity through the practice, which influenced both his songwriting and his personal life. The song “Within You Without You” reflects his spiritual journey and the peace he found through TM. The recording marked a significant departure from the Beatles' previous work; musically, it evokes the Indian devotional tradition, while the overtly spiritual quality of the lyrics reflects Harrison's absorption in Hindu philosophy.
Mindfulness and Meditation
Mindfulness and meditation have become increasingly popular among musicians seeking to maintain their mental health. These practices help individuals stay grounded, reduce stress, and improve overall well-being. George Harrison’s embrace of TM is a prime example of how mindfulness can transform a creative person's life.
Harrison’s dedication to TM didn’t just help him personally; it also profoundly impacted his music. His incorporation of Indian instruments and philosophical themes into his songs brought a new dimension to The Beatles’ music and left an enduring legacy in the music world. By finding a healthy outlet in meditation, Harrison could navigate the challenges of fame and continue creating impactful music.
The Power of Community
Siegel Alonso notes that another vital aspect of mental health is the strength of community. Like all individuals, musicians need a support system. Whether it’s fellow bandmates, family, friends, or mental health professionals, having people to lean on can make a significant difference.
John Frusciante’s return to the Red Hot Chili Peppers is a testament to the importance of community. His bandmates supported him through his recovery, and their familial bond played a vital role in his comeback. The collaborative nature of music itself fosters a sense of belonging and mutual support, which is critical for mental health.
Moving Forward
The music industry has made strides in recent years to address mental health more openly. Initiatives like MusiCares provide resources and support for musicians dealing with mental health issues. However, there is still much work to be done. Shattering the stigma around mental health and fostering open conversations are key steps toward a healthier industry.
Musicians like John Frusciante and George Harrison show us that recovery and well-being are possible, even though the journey may be challenging. By seeking help, embracing mindfulness, and finding healthy outlets for expression, musicians can navigate their challenges and continue to inspire us with their art.
In conclusion, mental health in the music industry is a complex issue. Still, with the right coping strategies and support systems, Daniel Siegel Alonso posits that it is achievable to overcome the challenges. As fans and listeners, we can also play a role by supporting initiatives promoting mental health and recognizing the humanity behind the music we cherish. After all, the well-being of the artists who create the soundtrack of our lives is just as important as the music itself.
-
 @ 4961e68d:a2212e1c
2025-05-02 07:47:16
@ 4961e68d:a2212e1c
2025-05-02 07:47:16热死人了
-
 @ 1c19eb1a:e22fb0bc
2025-04-30 22:02:13
@ 1c19eb1a:e22fb0bc
2025-04-30 22:02:13I am happy to present to you the first full review posted to Nostr Reviews: #Primal for #Android!
Primal has its origins as a micro-blogging, social media client, though it is now expanding its horizons into long-form content. It was first released only as a web client in March of 2023, but has since had a native client released for both iOS and Android. All of Primal's clients recently had an update to Primal 2.0, which included both performance improvements and a number of new features. This review will focus on the Android client specifically, both on phone and tablet.
Since Primal has also added features that are only available to those enrolled in their new premium subscription, it should also be noted that this review will be from the perspective of a free user. This is for two reasons. First, I am using an alternate npub to review the app, and if I were to purchase premium at some time in the future, it would be on my main npub. Second, despite a lot of positive things I have to say about Primal, I am not planning to regularly use any of their apps on my main account for the time being, for reasons that will be discussed later in the review.
The application can be installed through the Google Play Store, nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8, or by downloading it directly from Primal's GitHub. The full review is current as of Primal Android version 2.0.21. Updates to the review on 4/30/2025 are current as of version 2.2.13.
In the ecosystem of "notes and other stuff," Primal is predominantly in the "notes" category. It is geared toward users who want a social media experience similar to Twitter or Facebook with an infinite scrolling feed of notes to interact with. However, there is some "other stuff" included to complement this primary focus on short and long form notes including a built-in Lightning wallet powered by #Strike, a robust advanced search, and a media-only feed.
Overall Impression
Score: 4.4 / 5 (Updated 4/30/2025)
Primal may well be the most polished UI of any Nostr client native to Android. It is incredibly well designed and thought out, with all of the icons and settings in the places a user would expect to find them. It is also incredibly easy to get started on Nostr via Primal's sign-up flow. The only two things that will be foreign to new users are the lack of any need to set a password or give an email address, and the prompt to optionally set up the wallet.
Complaints prior to the 2.0 update about Primal being slow and clunky should now be completely alleviated. I only experienced quick load times and snappy UI controls with a couple very minor exceptions, or when loading DVM-based feeds, which are outside of Primal's control.
Primal is not, however, a client that I would recommend for the power-user. Control over preferred relays is minimal and does not allow the user to determine which relays they write to and which they only read from. Though you can use your own wallet, it will not appear within the wallet interface, which only works with the custodial wallet from Strike. Moreover, and most eggregiously, the only way for existing users to log in is by pasting their nsec, as Primal does not support either the Android signer or remote signer options for users to protect their private key at this time. This lack of signer support is the primary reason the client received such a low overall score. If even one form of external signer log in is added to Primal, the score will be amended to 4.2 / 5, and if both Android signer and remote signer support is added, it will increase to 4.5.
Update: As of version 2.2.13, Primal now supports the Amber Android signer! One of the most glaring issues with the app has now been remedied and as promised, the overall score above has been increased.
Another downside to Primal is that it still utilizes an outdated direct message specification that leaks metadata that can be readily seen by anyone on the network. While the content of your messages remains encrypted, anyone can see who you are messaging with, and when. This also means that you will not see any DMs from users who are messaging from a client that has moved to the latest, and far more private, messaging spec.
That said, the beautiful thing about Nostr as a protocol is that users are not locked into any particular client. You may find Primal to be a great client for your average #bloomscrolling and zapping memes, but opt for a different client for more advanced uses and for direct messaging.
Features
Primal has a lot of features users would expect from any Nostr client that is focused on short-form notes, but it also packs in a lot of features that set it apart from other clients, and that showcase Primal's obvious prioritization of a top-tier user experience.
Home Feed
By default, the infinitely scrolling Home feed displays notes from those you currently follow in chronological order. This is traditional Nostr at its finest, and made all the more immersive by the choice to have all distracting UI elements quickly hide themselves from view as the you begin to scroll down the feed. They return just as quickly when you begin to scroll back up.
Scrolling the feed is incredibly fast, with no noticeable choppiness and minimal media pop-in if you are on a decent internet connection.
Helpfully, it is easy to get back to the top of the feed whenever there is a new post to be viewed, as a bubble will appear with the profile pictures of the users who have posted since you started scrolling.

Interacting With Notes
Interacting with a note in the feed can be done via the very recognizable icons at the bottom of each post. You can comment, zap, like, repost, and/or bookmark the note.
Notably, tapping on the zap icon will immediately zap the note your default amount of sats, making zapping incredibly fast, especially when using the built-in wallet. Long pressing on the zap icon will open up a menu with a variety of amounts, along with the ability to zap a custom amount. All of these amounts, and the messages that are sent with the zap, can be customized in the application settings.
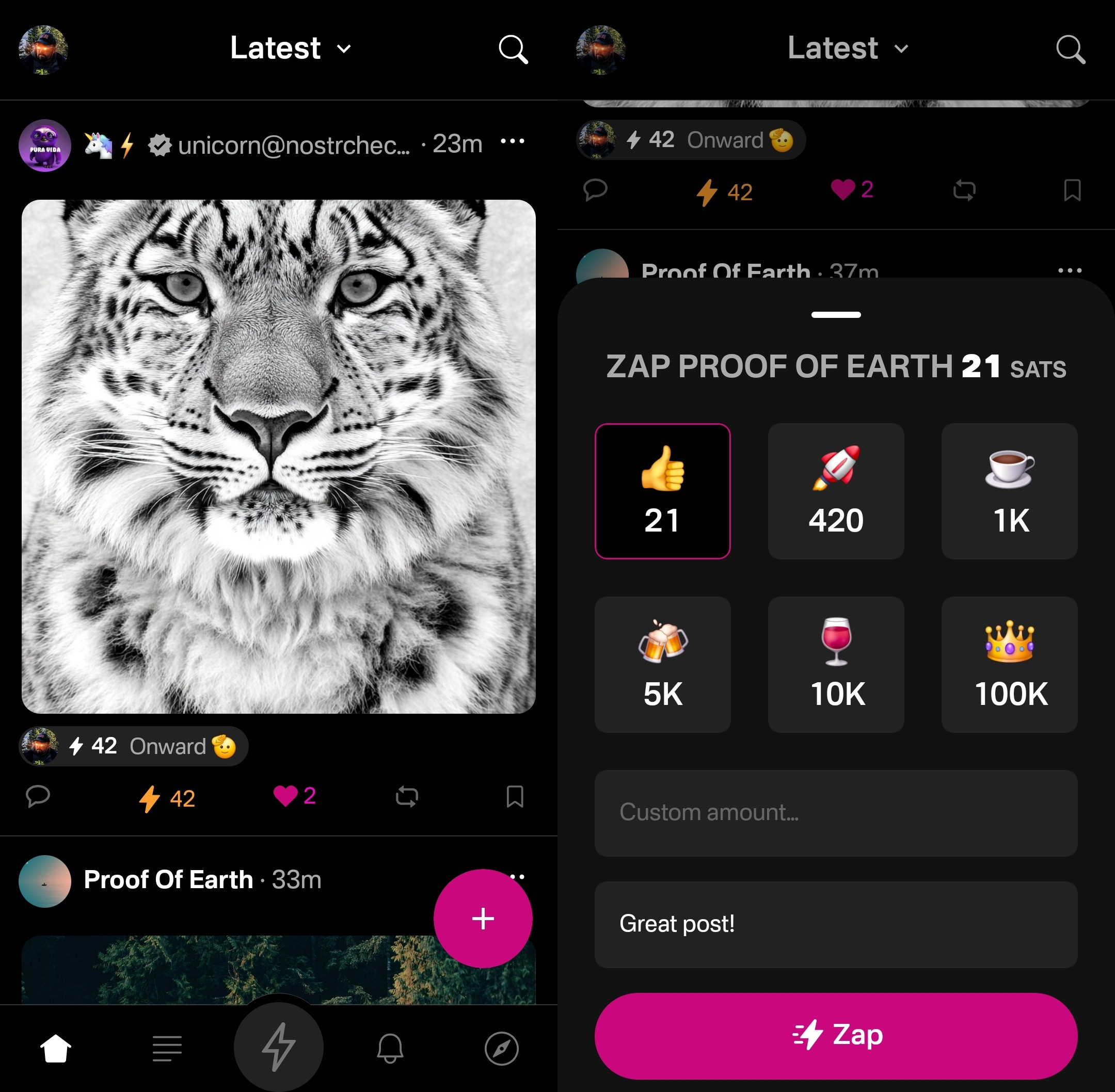
Users who are familiar with Twitter or Instagram will feel right at home with only having one option for "liking" a post. However, users from Facebook or other Nostr clients may wonder why they don't have more options for reactions. This is one of those things where users who are new to Nostr probably won't notice they are missing out on anything at all, while users familiar with clients like #Amethyst or #noStrudel will miss the ability to react with a 🤙 or a 🫂.
It's a similar story with the bookmark option. While this is a nice bit of feature parity for Twitter users, for those already used to the ability to have multiple customized lists of bookmarks, or at minimum have the ability to separate them into public and private, it may be a disappointment that they have no access to the bookmarks they already built up on other clients. Primal offers only one list of bookmarks for short-form notes and they are all visible to the public. However, you are at least presented with a warning about the public nature of your bookmarks before saving your first one.
Yet, I can't dock the Primal team much for making these design choices, as they are understandable for Primal's goal of being a welcoming client for those coming over to Nostr from centralized platforms. They have optimized for the onboarding of new users, rather than for those who have been around for a while, and there is absolutely nothing wrong with that.
Post Creation
Composing posts in Primal is as simple as it gets. Accessed by tapping the obvious circular button with a "+" on it in the lower right of the Home feed, most of what you could need is included in the interface, and nothing you don't.
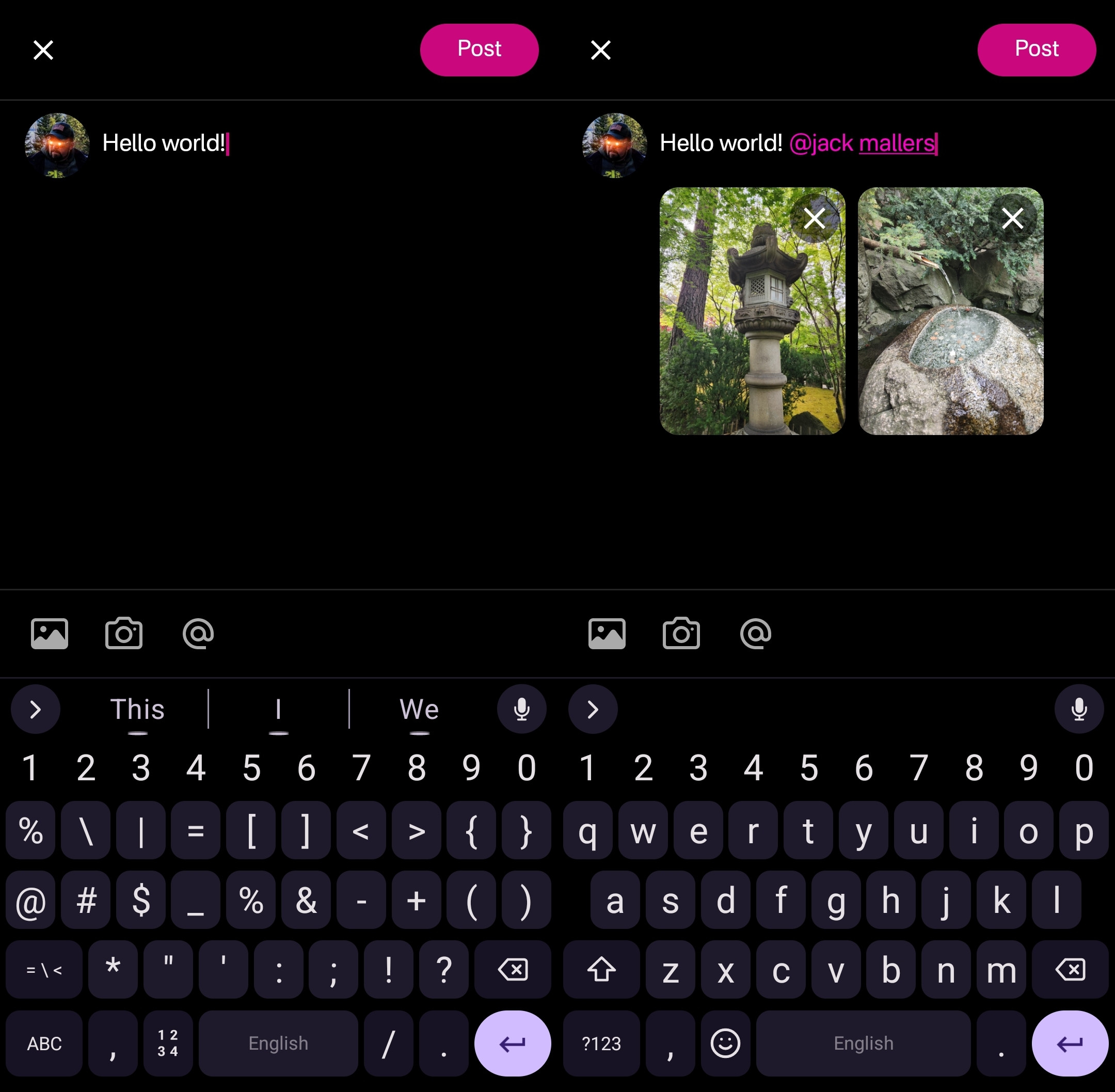
Your device's default keyboard loads immediately, and the you can start typing away.
There are options for adding images from your gallery, or taking a picture with your camera, both of which will result in the image being uploaded to Primal's media-hosting server. If you prefer to host your media elsewhere, you can simply paste the link to that media into your post.
There is also an @ icon as a tip-off that you can tag other users. Tapping on this simply types "@" into your note and brings up a list of users. All you have to do to narrow down the user you want to tag is continue typing their handle, Nostr address, or paste in their npub.
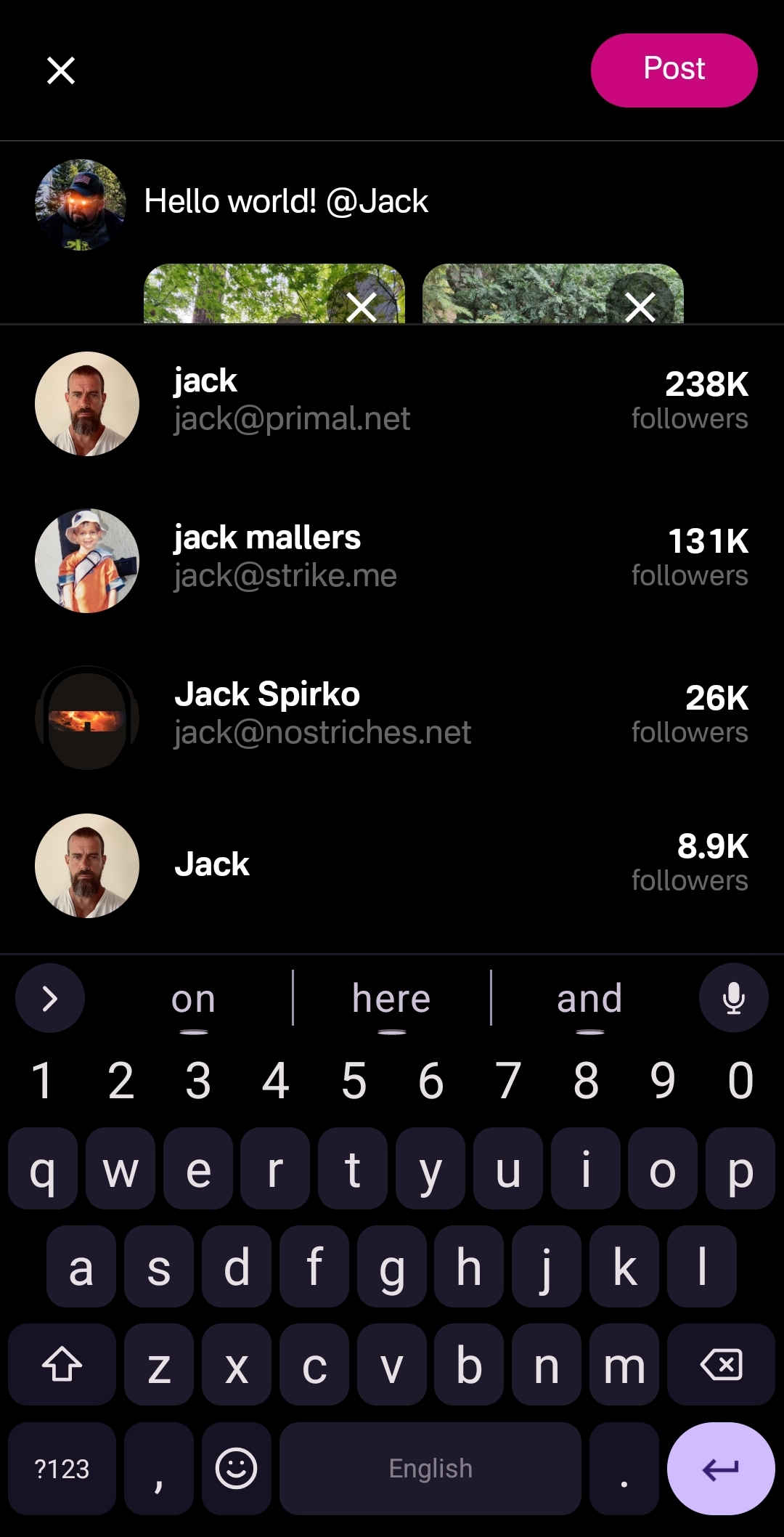
This can get mixed results in other clients, which sometimes have a hard time finding particular users when typing in their handle, forcing you to have to remember their Nostr address or go hunt down their npub by another means. Not so with Primal, though. I had no issues tagging anyone I wanted by simply typing in their handle.
Of course, when you are tagging someone well known, you may find that there are multiple users posing as that person. Primal helps you out here, though. Usually the top result is the person you want, as Primal places them in order of how many followers they have. This is quite reliable right now, but there is nothing stopping someone from spinning up an army of bots to follow their fake accounts, rendering follower count useless for determining which account is legitimate. It would be nice to see these results ranked by web-of-trust, or at least an indication of how many users you follow who also follow the users listed in the results.
Once you are satisfied with your note, the "Post" button is easy to find in the top right of the screen.
Feed Selector and Marketplace
Primal's Home feed really shines when you open up the feed selection interface, and find that there are a plethora of options available for customizing your view. By default, it only shows four options, but tapping "Edit" opens up a new page of available toggles to add to the feed selector.
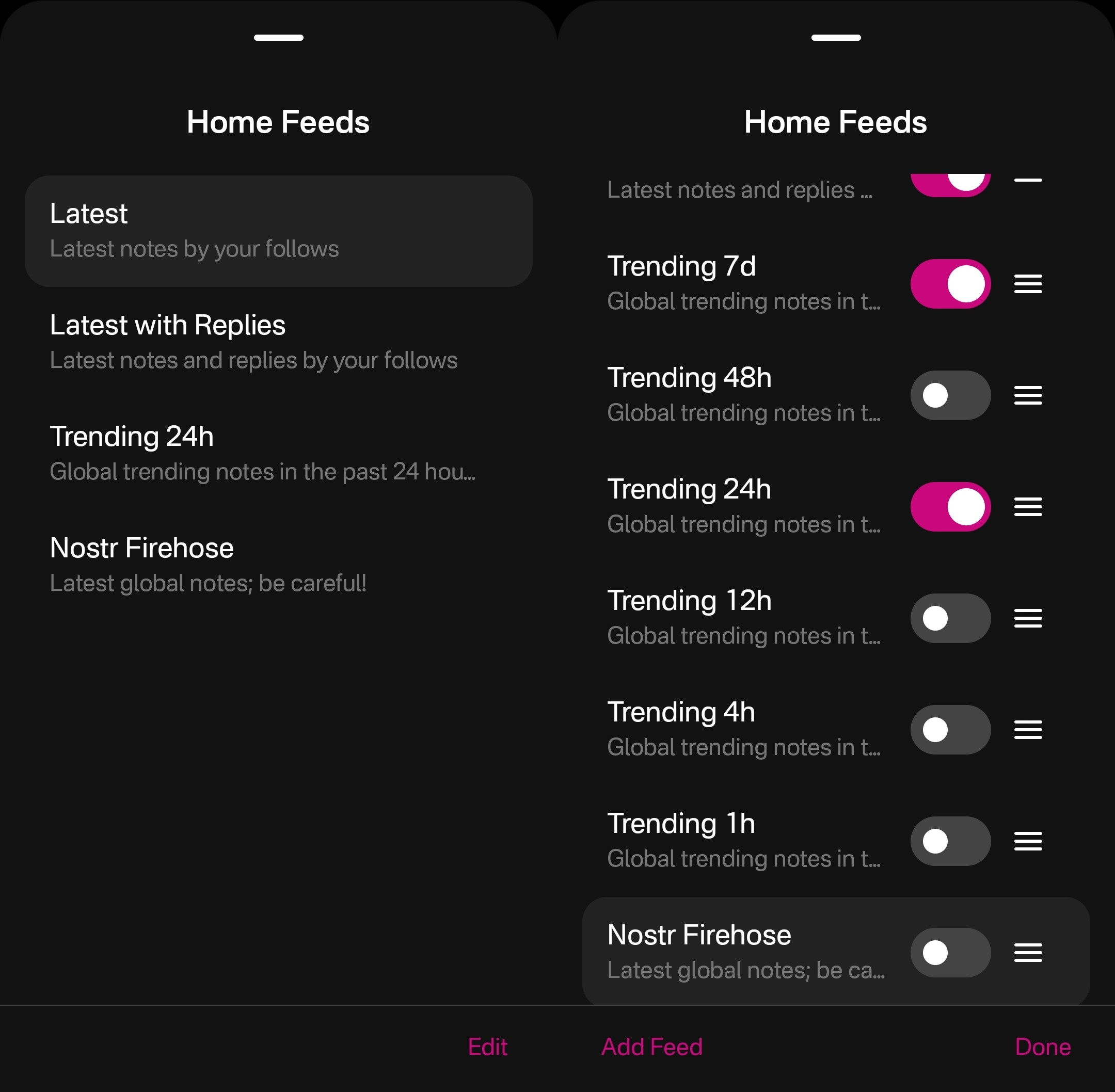
The options don't end there, though. Tapping "Add Feed" will open up the feed marketplace, where an ever-growing number of custom feeds can be found, some created by Primal and some created by others. This feed marketplace is available to a few other clients, but none have so closely integrated it with their Home feeds like Primal has.
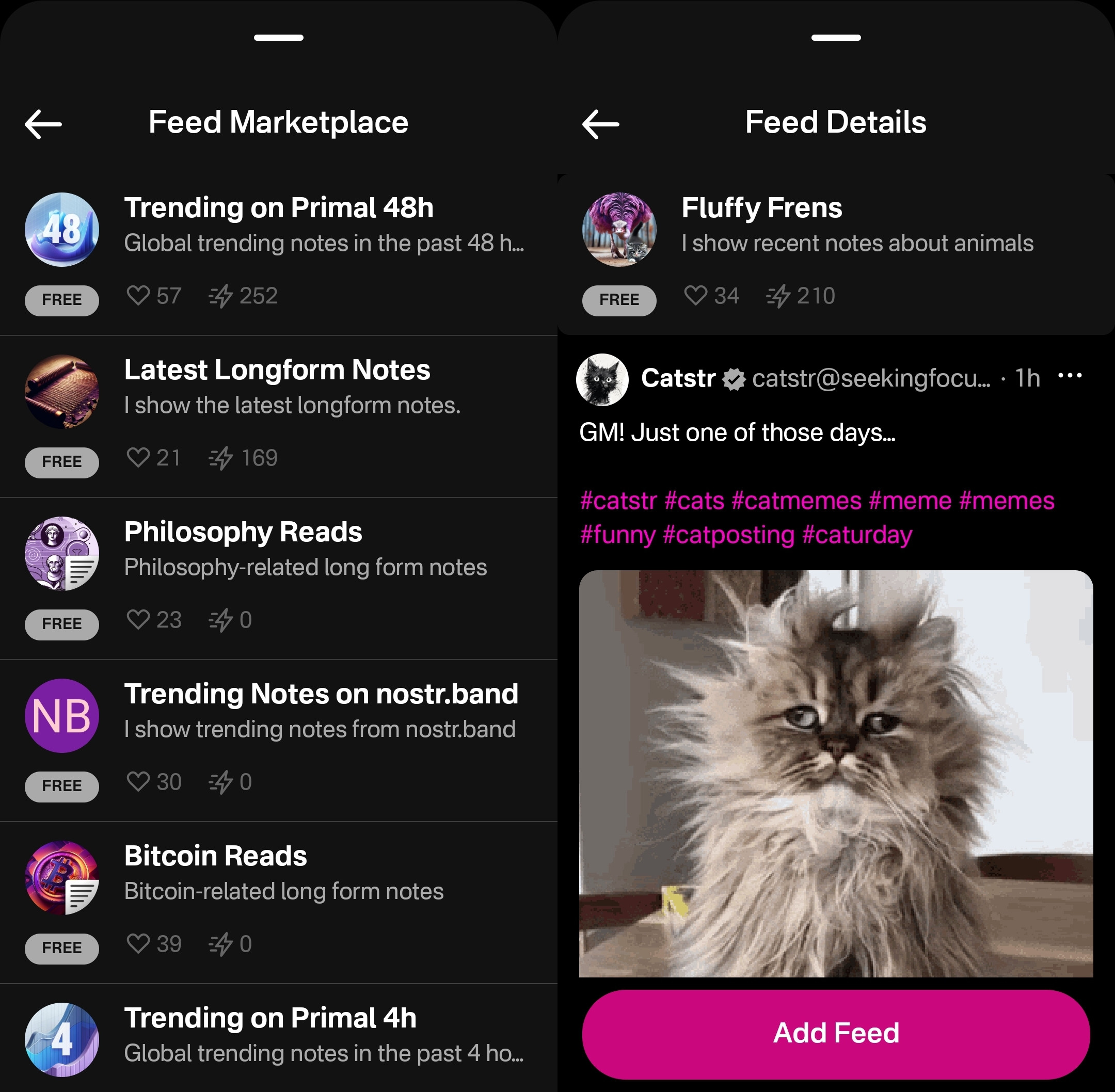
Unfortunately, as great as these custom feeds are, this was also the feature where I ran into the most bugs while testing out the app.
One of these bugs was while selecting custom feeds. Occasionally, these feed menu screens would become unresponsive and I would be unable to confirm my selection, or even use the back button on my device to back out of the screen. However, I was able to pull the screen down to close it and re-open the menu, and everything would be responsive again.
This only seemed to occur when I spent 30 seconds or more on the same screen, so I imagine that most users won't encounter it much in their regular use.
Another UI bug occurred for me while in the feed marketplace. I could scroll down the list of available feeds, but attempting to scroll back up the feed would often close the interface entirely instead, as though I had pulled the screen down from the top, when I was swiping in the middle of the screen.
The last of these bugs occurred when selecting a long-form "Reads" feed while in the menu for the Home feed. The menu would allow me to add this feed and select it to be displayed, but it would fail to load the feed once selected, stating "There is no content in this feed." Going to a different page within the the app and then going back to the Home tab would automatically remove the long-form feed from view, and reset back to the most recently viewed short-form "Notes" feed, though the long-form feed would still be available to select again. The results were similar when selecting a short-form feed for the Reads feed.
I would suggest that if long-form and short-form feeds are going to be displayed in the same list, and yet not be able to be displayed in the same feed, the application should present an error message when attempting to add a long-form feed for the Home feed or a short-form feed for the Reads feed, and encourage the user add it to the proper feed instead.
Long-Form "Reads" Feed
A brand new feature in Primal 2.0, users can now browse and read long-form content posted to Nostr without having to go to a separate client. Primal now has a dedicated "Reads" feed to browse and interact with these articles.
This feed displays the author and title of each article or blog, along with an image, if available. Quite conveniently, it also lets you know the approximate amount of time it will take to read a given article, so you can decide if you have the time to dive into it now, or come back later.
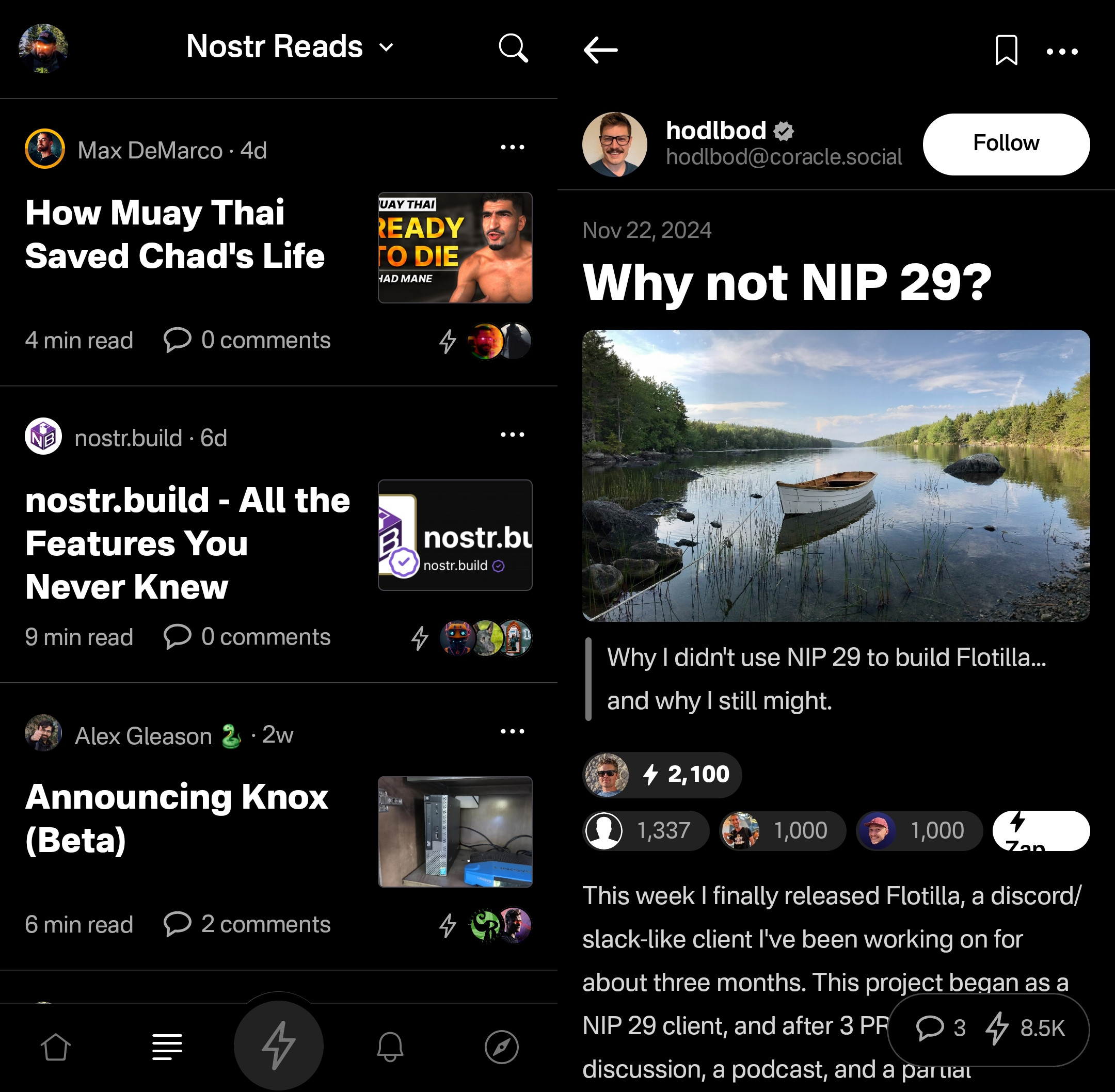
Noticeably absent from the Reads feed, though, is the ability to compose an article of your own. This is another understandable design choice for a mobile client. Composing a long-form note on a smart-phone screen is not a good time. Better to be done on a larger screen, in a client with a full-featured text editor.
Tapping an article will open up an attractive reading interface, with the ability to bookmark for later. These bookmarks are a separate list from your short-form note bookmarks so you don't have to scroll through a bunch of notes you bookmarked to find the article you told yourself you would read later and it's already been three weeks.
While you can comment on the article or zap it, you will notice that you cannot repost or quote-post it. It's not that you can't do so on Nostr. You absolutely can in other clients. In fact, you can do so on Primal's web client, too. However, Primal on Android does not handle rendering long-form note previews in the Home feed, so they have simply left out the option to share them there. See below for an example of a quote-post of a long-form note in the Primal web client vs the Android client.
Primal Web:
Primal Android:
The Explore Tab
Another unique feature of the Primal client is the Explore tab, indicated by the compass icon. This tab is dedicated to discovering content from outside your current follow list. You can find the feed marketplace here, and add any of the available feeds to your Home or Reads feed selections. You can also find suggested users to follow in the People tab. The Zaps tab will show you who has been sending and receiving large zaps. Make friends with the generous ones!
The Media tab gives you a chronological feed of just media, displayed in a tile view. This can be great when you are looking for users who post dank memes, or incredible photography on a regular basis. Unfortunately, it appears that there is no way to filter this feed for sensitive content, and so you do not have to scroll far before you see pornographic material.
Indeed, it does not appear that filters for sensitive content are available in Primal for any feed. The app is kind enough to give a minimal warning that objectionable content may be present when selecting the "Nostr Firehose" option in your Home feed, with a brief "be careful" in the feed description, but there is not even that much of a warning here for the media-only feed.
The media-only feed doesn't appear to be quite as bad as the Nostr Firehose feed, so there must be some form of filtering already taking place, rather than being a truly global feed of all media. Yet, occasional sensitive content still litters the feed and is unavoidable, even for users who would rather not see it. There are, of course, ways to mute particular users who post such content, if you don't want to see it a second time from the same user, but that is a never-ending game of whack-a-mole, so your only realistic choices in Primal are currently to either avoid the Nostr Firehose and media-only feeds, or determine that you can put up with regularly scrolling past often graphic content.
This is probably the only choice Primal has made that is not friendly to new users. Most clients these days will have some protections in place to hide sensitive content by default, but still allow the user to toggle those protections off if they so choose. Some of them hide posts flagged as sensitive content altogether, others just blur the images unless the user taps to reveal them, and others simply blur all images posted by users you don't follow. If Primal wants to target new users who are accustomed to legacy social media platforms, they really should follow suit.
The final tab is titled "Topics," but it is really just a list of popular hashtags, which appear to be arranged by how often they are being used. This can be good for finding things that other users are interested in talking about, or finding specific content you are interested in.
If you tap on any topic in the list, it will display a feed of notes that include that hashtag. What's better, you can add it as a feed option you can select on your Home feed any time you want to see posts with that tag.
The only suggestion I would make to improve this tab is some indication of why the topics are arranged in the order presented. A simple indicator of the number of posts with that hashtag in the last 24 hours, or whatever the interval is for determining their ranking, would more than suffice.
Even with those few shortcomings, Primal's Explore tab makes the client one of the best options for discovering content on Nostr that you are actually interested in seeing and interacting with.
Built-In Wallet
While this feature is completely optional, the icon to access the wallet is the largest of the icons at the bottom of the screen, making you feel like you are missing out on the most important feature of the app if you don't set it up. I could be critical of this design choice, but in many ways I think it is warranted. The built-in wallet is one of the most unique features that Primal has going for it.
Consider: If you are a new user coming to Nostr, who isn't already a Bitcoiner, and you see that everyone else on the platform is sending and receiving sats for their posts, will you be more likely to go download a separate wallet application or use one that is built-into your client? I would wager the latter option by a long shot. No need to figure out which wallet you should download, whether you should do self-custody or custodial, or make the mistake of choosing a wallet with unexpected setup fees and no Lightning address so you can't even receive zaps to it. nostr:npub16c0nh3dnadzqpm76uctf5hqhe2lny344zsmpm6feee9p5rdxaa9q586nvr often states that he believes more people will be onboarded to Bitcoin through Nostr than by any other means, and by including a wallet into the Primal client, his team has made adopting Bitcoin that much easier for new Nostr users.
Some of us purists may complain that it is custodial and KYC, but that is an unfortunate necessity in order to facilitate onboarding newcoiners to Bitcoin. This is not intended to be a wallet for those of us who have been using Bitcoin and Lightning regularly already. It is meant for those who are not already familiar with Bitcoin to make it as easy as possible to get off zero, and it accomplishes this better than any other wallet I have ever tried.
In large part, this is because the KYC is very light. It does need the user's legal name, a valid email address, date of birth, and country of residence, but that's it! From there, the user can buy Bitcoin directly through the app, but only in the amount of $4.99 at a time. This is because there is a substantial markup on top of the current market price, due to utilizing whatever payment method the user has set up through their Google Play Store. The markup seemed to be about 19% above the current price, since I could purchase 4,143 sats for $4.99 ($120,415 / Bitcoin), when the current price was about $101,500. But the idea here is not for the Primal wallet to be a user's primary method of stacking sats. Rather, it is intended to get them off zero and have a small amount of sats to experience zapping with, and it accomplishes this with less friction than any other method I know.
Moreover, the Primal wallet has the features one would expect from any Lightning wallet. You can send sats to any Nostr user or Lightning address, receive via invoice, or scan to pay an invoice. It even has the ability to receive via on-chain. This means users who don't want to pay the markup from buying through Primal can easily transfer sats they obtained by other means into the Primal wallet for zapping, or for using it as their daily-driver spending wallet.
Speaking of zapping, once the wallet is activated, sending zaps is automatically set to use the wallet, and they are fast. Primal gives you immediate feedback that the zap was sent and the transaction shows in your wallet history typically before you can open the interface. I can confidently say that Primal wallet's integration is the absolute best zapping experience I have seen in any Nostr client.
One thing to note that may not be immediately apparent to new users is they need to add their Lightning address with Primal into their profile details before they can start receiving zaps. So, sending zaps using the wallet is automatic as soon as you activate it, but receiving is not. Ideally, this could be further streamlined, so that Primal automatically adds the Lightning address to the user's profile when the wallet is set up, so long as there is not currently a Lightning address listed.
Of course, if you already have a Lightning wallet, you can connect it to Primal for zapping, too. We will discuss this further in the section dedicated to zap integration.
Advanced Search
Search has always been a tough nut to crack on Nostr, since it is highly dependent on which relays the client is pulling information from. Primal has sought to resolve this issue, among others, by running a caching relay that pulls notes from a number of relays to store them locally, and perform some spam filtering. This allows for much faster retrieval of search results, and also makes their advanced search feature possible.
Advanced search can be accessed from most pages by selecting the magnifying glass icon, and then the icon for more options next to the search bar.
As can be seen in the screenshot below, there are a plethora of filters that can be applied to your search terms.
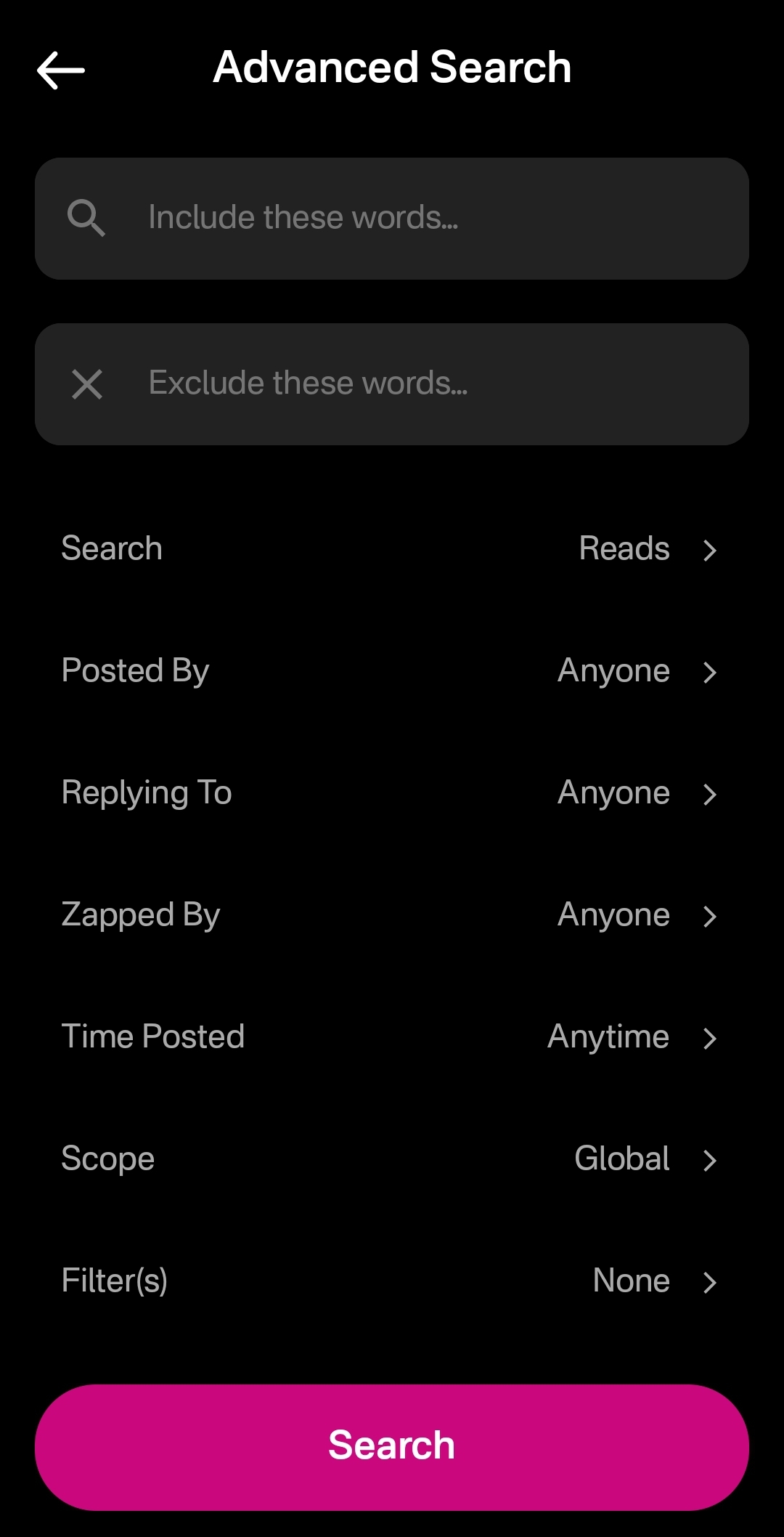
You can immediately see how this advanced search could be a very powerful tool for not just finding a particular previous note that you are looking for, but for creating your own custom feed of notes. Well, wouldn't you know it, Primal allows you to do just that! This search feature, paired with the other features mentioned above related to finding notes you want to see in your feed, makes Primal hands-down the best client for content discovery.
The only downside as a free user is that some of these search options are locked behind the premium membership. Or else you only get to see a certain number of results of your advanced search before you must be a premium member to see more.
Can My Grandma Use It?
Score: 4.8 / 5 Primal has obviously put a high priority on making their client user-friendly, even for those who have never heard of relays, public/private key cryptography, or Bitcoin. All of that complexity is hidden away. Some of it is available to play around with for the users who care to do so, but it does not at all get in the way of the users who just want to jump in and start posting notes and interacting with other users in a truly open public square.
To begin with, the onboarding experience is incredibly smooth. Tap "Create Account," enter your chosen display name and optional bio information, upload a profile picture, and then choose some topics you are interested in. You are then presented with a preview of your profile, with the ability to add a banner image, if you so choose, and then tap "Create Account Now."
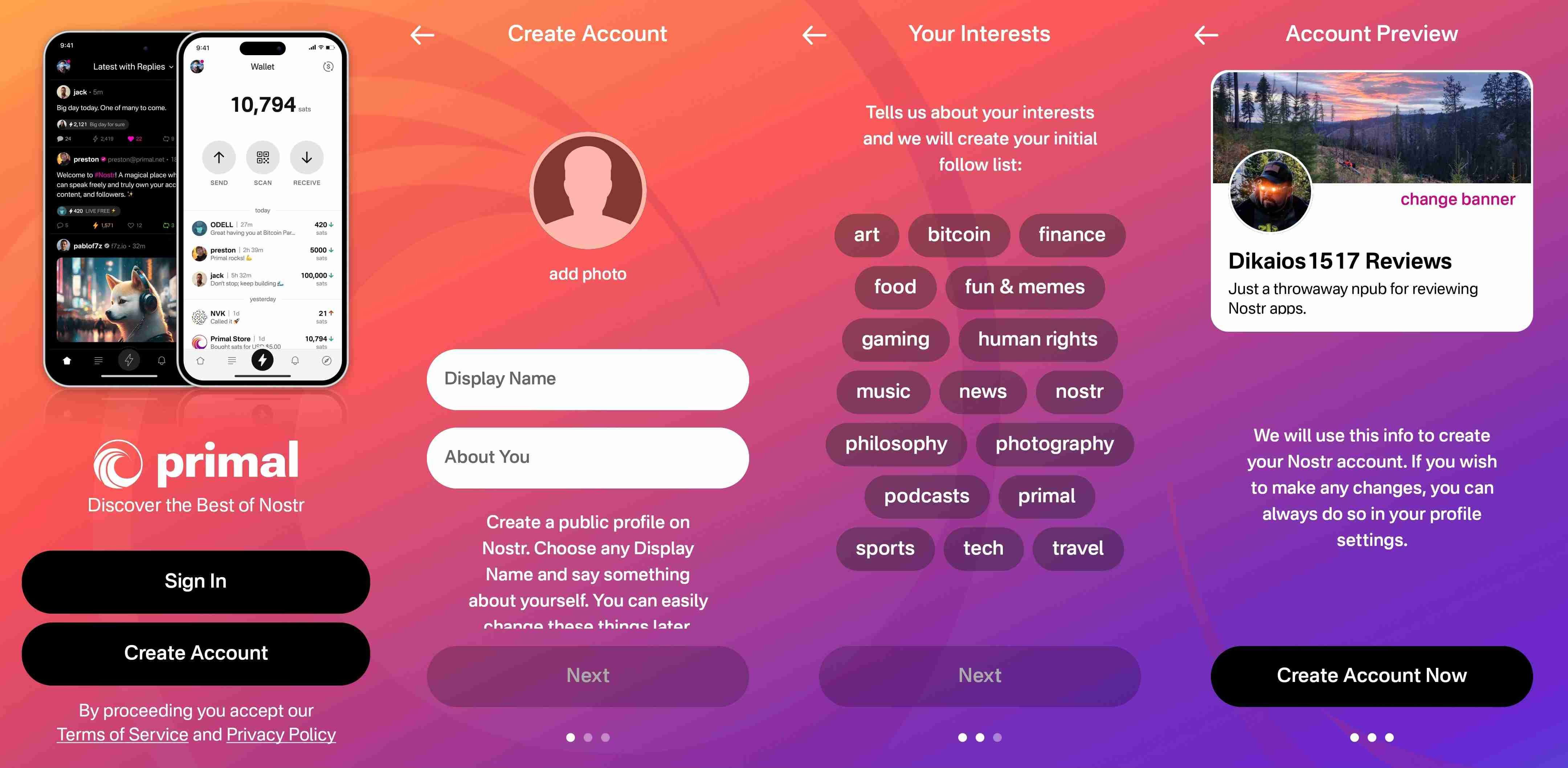
From there you receive confirmation that your account has been created and that your "Nostr key" is available to you in the application settings. No further explanation is given about what this key is for at this point, but the user doesn't really need to know at the moment, either. If they are curious, they will go to the app settings to find out.
At this point, Primal encourages the user to activate Primal Wallet, but also gives the option for the user to do it later.
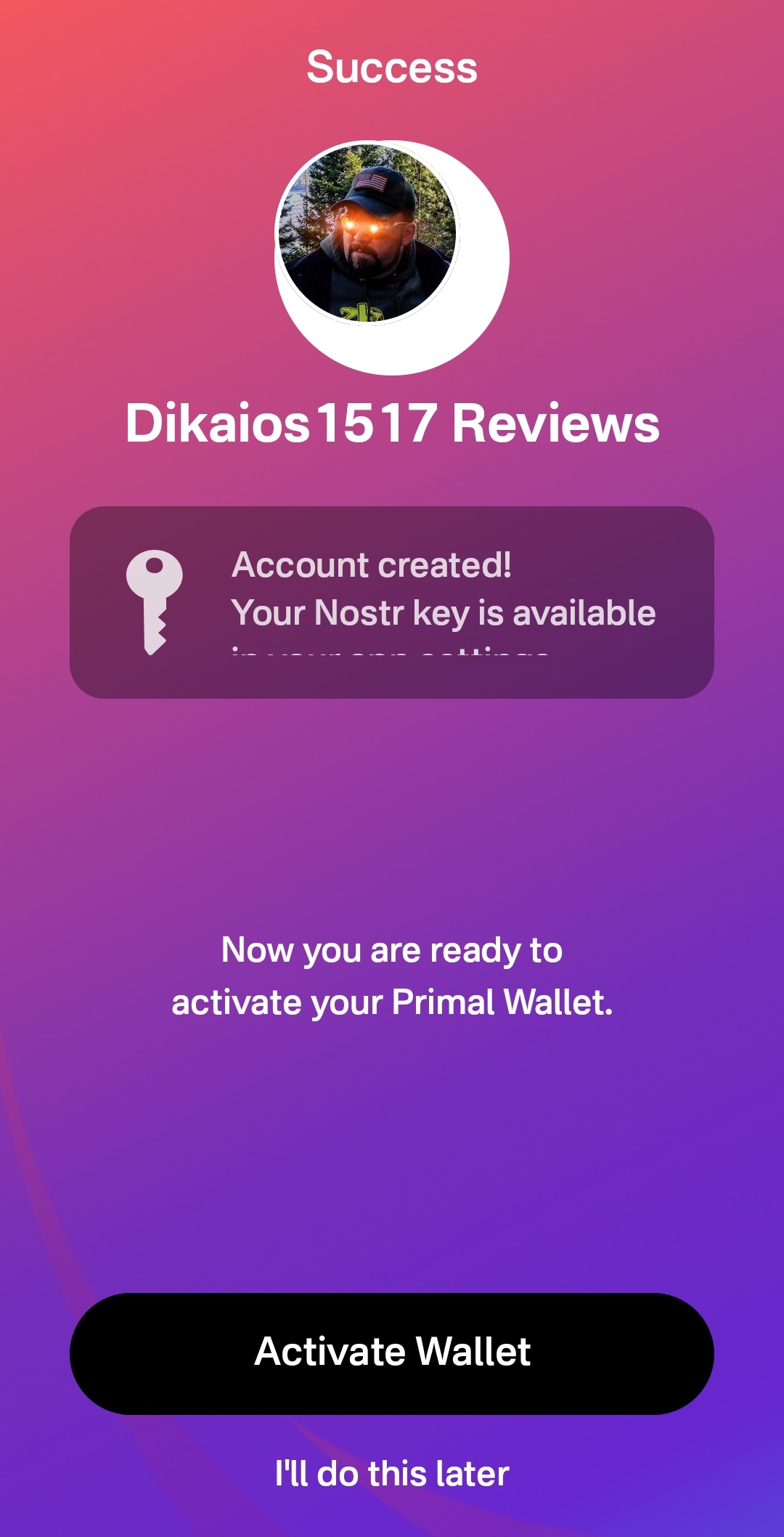
That's it! The next screen the user sees if they don't opt to set up the wallet is their Home feed with notes listed in chronological order. More impressive, the feed is not empty, because Primal has auto-followed several accounts based on your selected topics.
Now, there has definitely been some legitimate criticism of this practice of following specific accounts based on the topic selection, and I agree. I would much prefer to see Primal follow hashtags based on what was selected, and combine the followed hashtags into a feed titled "My Topics" or something of that nature, and make that the default view when the user finishes onboarding. Following particular users automatically will artificially inflate certain users' exposure, while other users who might be quality follows for that topic aren't seen at all.
The advantage of following particular users over a hashtag, though, is that Primal retains some control over the quality of the posts that new users are exposed to right away. Primal can ensure that new users see people who are actually posting quality photography when they choose it as one of their interests. However, even with that example, I chose photography as one of my interests and while I did get some stunning photography in my Home feed by default based on Primal's chosen follows, I also scrolled through the Photography hashtag for a bit and I really feel like I would have been better served if Primal had simply followed that hashtag rather than a particular set of users.
We've already discussed how simple it is to set up the Primal Wallet. You can see the features section above if you missed it. It is, by far, the most user friendly experience to onboarding onto Lightning and getting a few sats for zapping, and it is the only one I know of that is built directly into a Nostr client. This means new users will have a frictionless introduction to transacting via Lightning, perhaps without even realizing that's what they are doing.
Discovering new content of interest is incredibly intuitive on Primal, and the only thing that new users may struggle with is getting their own notes seen by others. To assist with this, I would suggest Primal encourage users to make their first post to the introductions hashtag and direct any questions to the AskNostr hashtag as part of the onboarding process. This will get them some immediate interactions from other users, and further encouragement to set up their wallet if they haven't already done so.
How do UI look?
Score: 4.9 / 5
Primal is the most stunningly beautiful Nostr client available, in my honest opinion. Despite some of my hangups about certain functionality, the UI alone makes me want to use it.
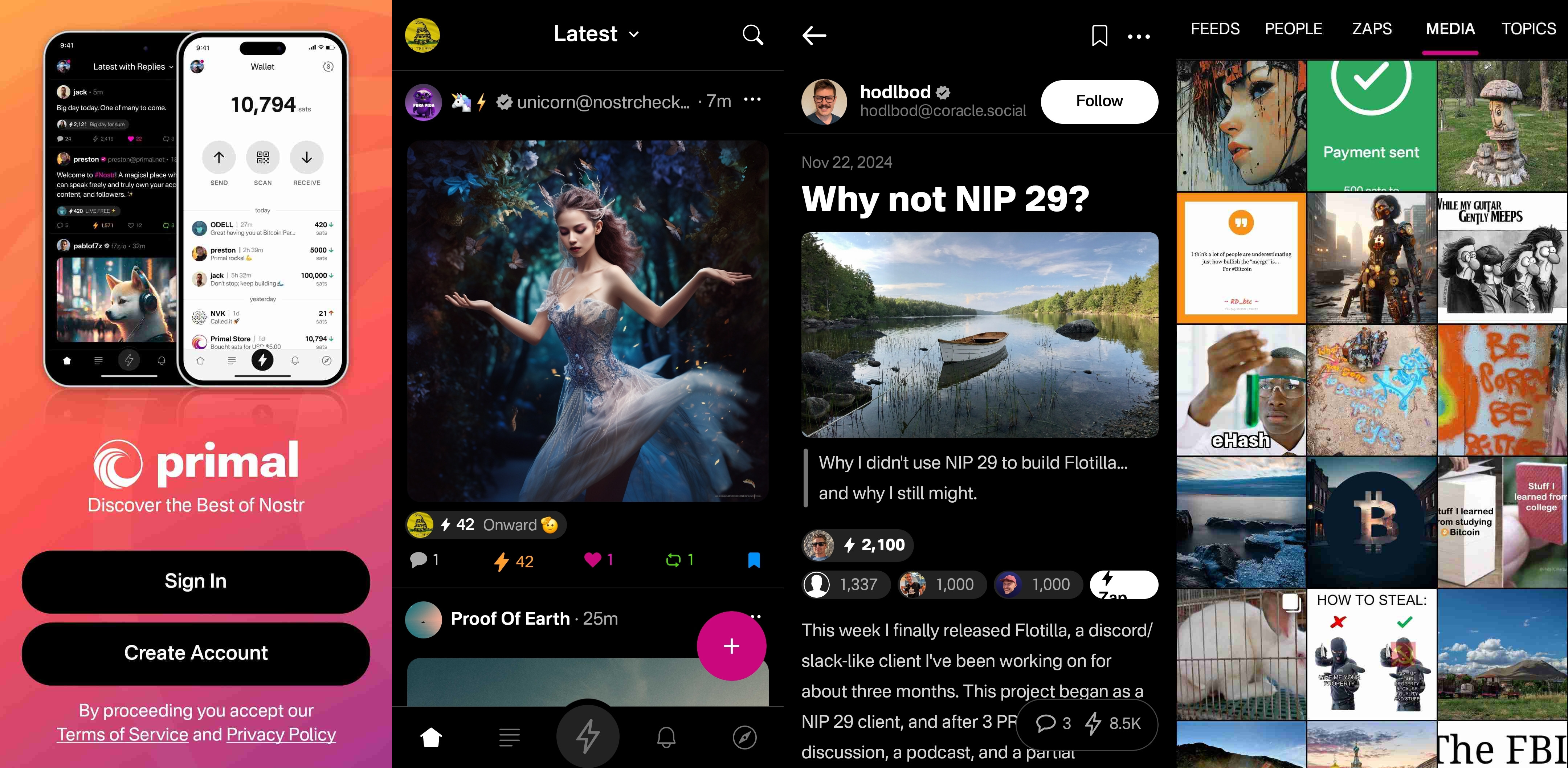
It is clean, attractive, and intuitive. Everything I needed was easy to find, and nothing felt busy or cluttered. There are only a few minor UI glitches that I ran into while testing the app. Some of them were mentioned in the section of the review detailing the feed selector feature, but a couple others occurred during onboarding.
First, my profile picture was not centered in the preview when I uploaded it. This appears to be because it was a low quality image. Uploading a higher quality photo did not have this result.

The other UI bug was related to text instructions that were cut off, and not able to scroll to see the rest of them. This occurred on a few pages during onboarding, and I expect it was due to the size of my phone screen, since it did not occur when I was on a slightly larger phone or tablet.
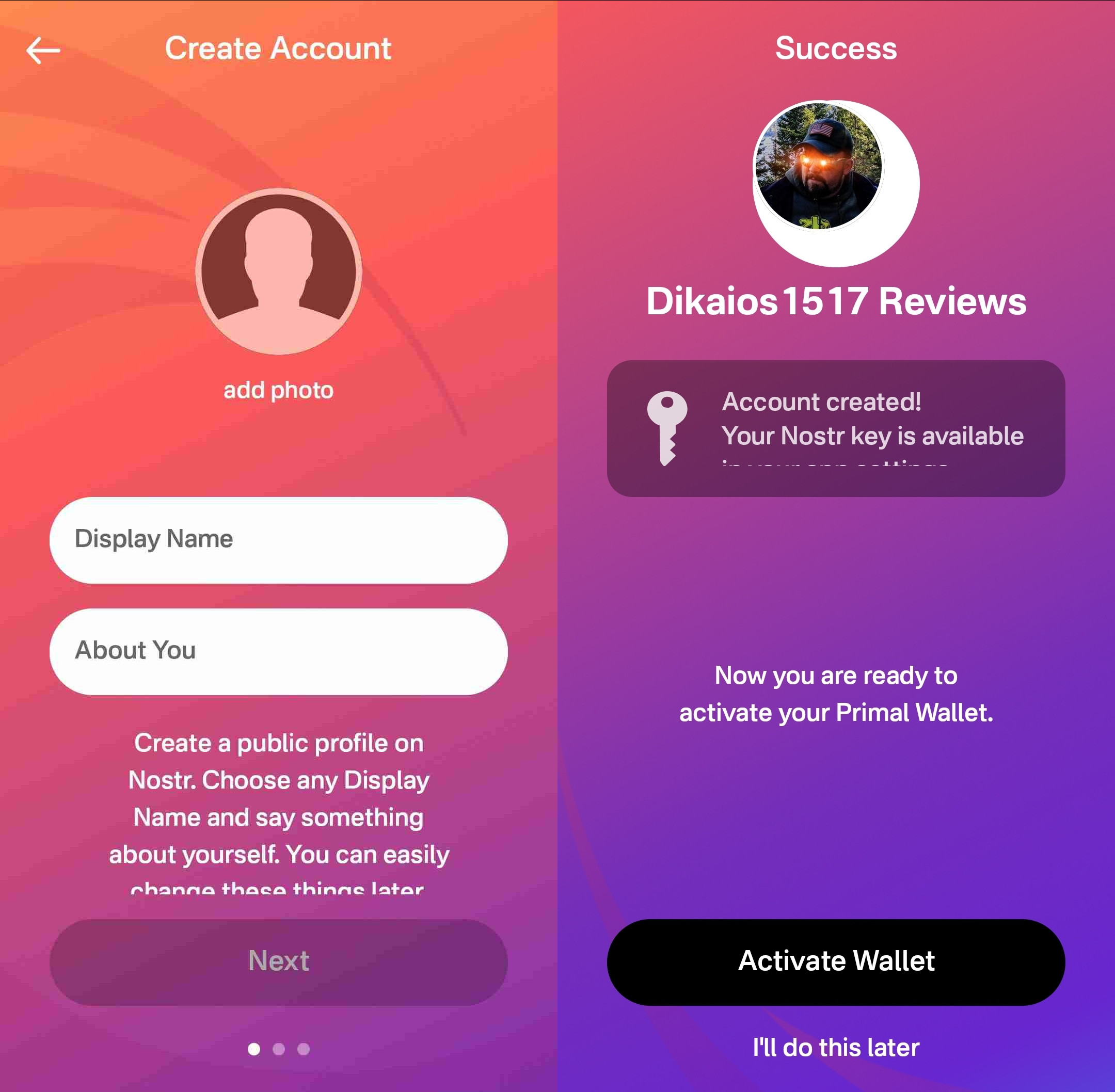
Speaking of tablets, Primal Android looks really good on a tablet, too! While the client does not have a landscape mode by default, many Android tablets support forcing apps to open in full-screen landscape mode, with mixed results. However, Primal handles it well. I would still like to see a tablet version developed that takes advantage of the increased screen real estate, but it is certainly a passable option.
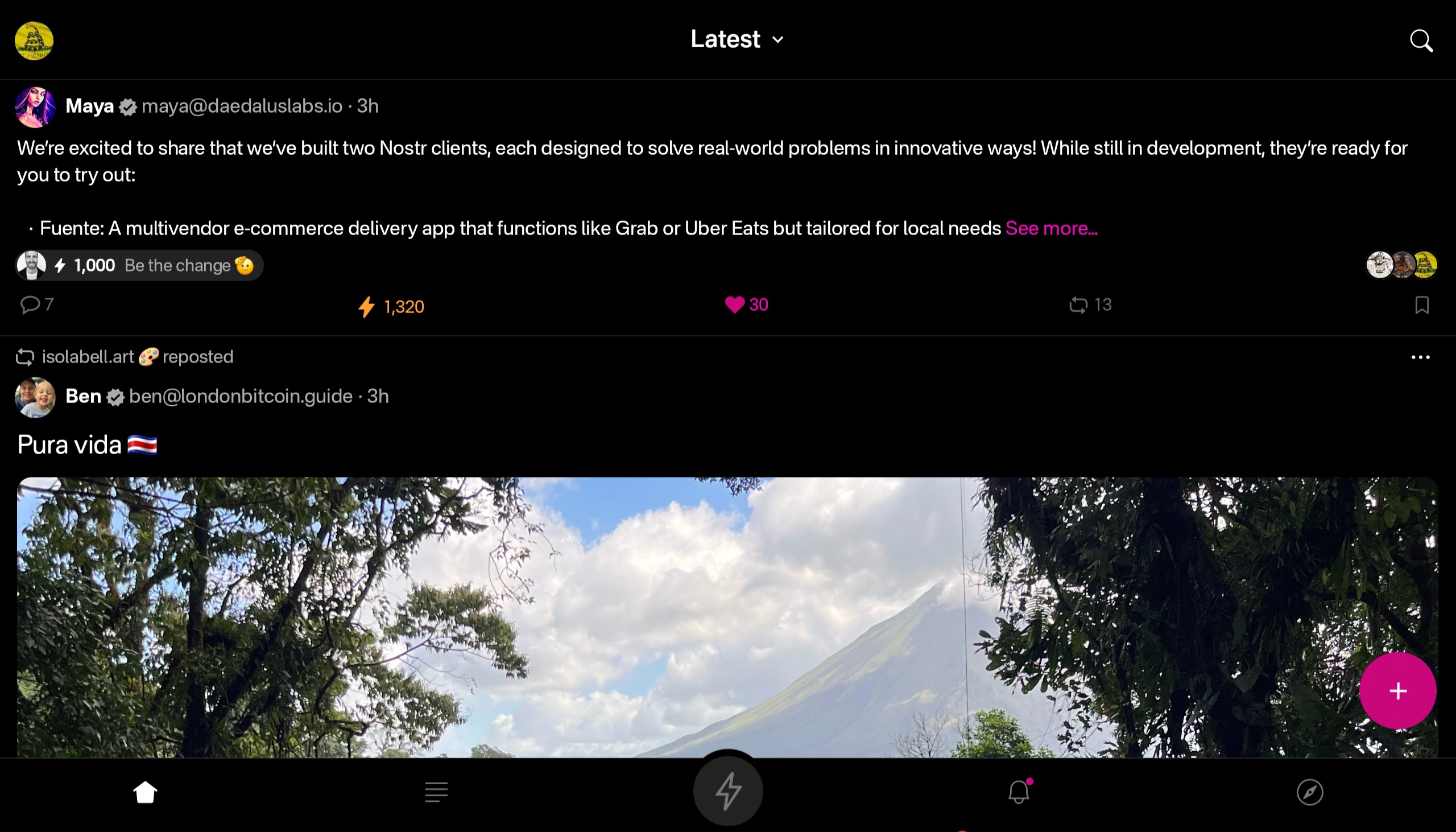

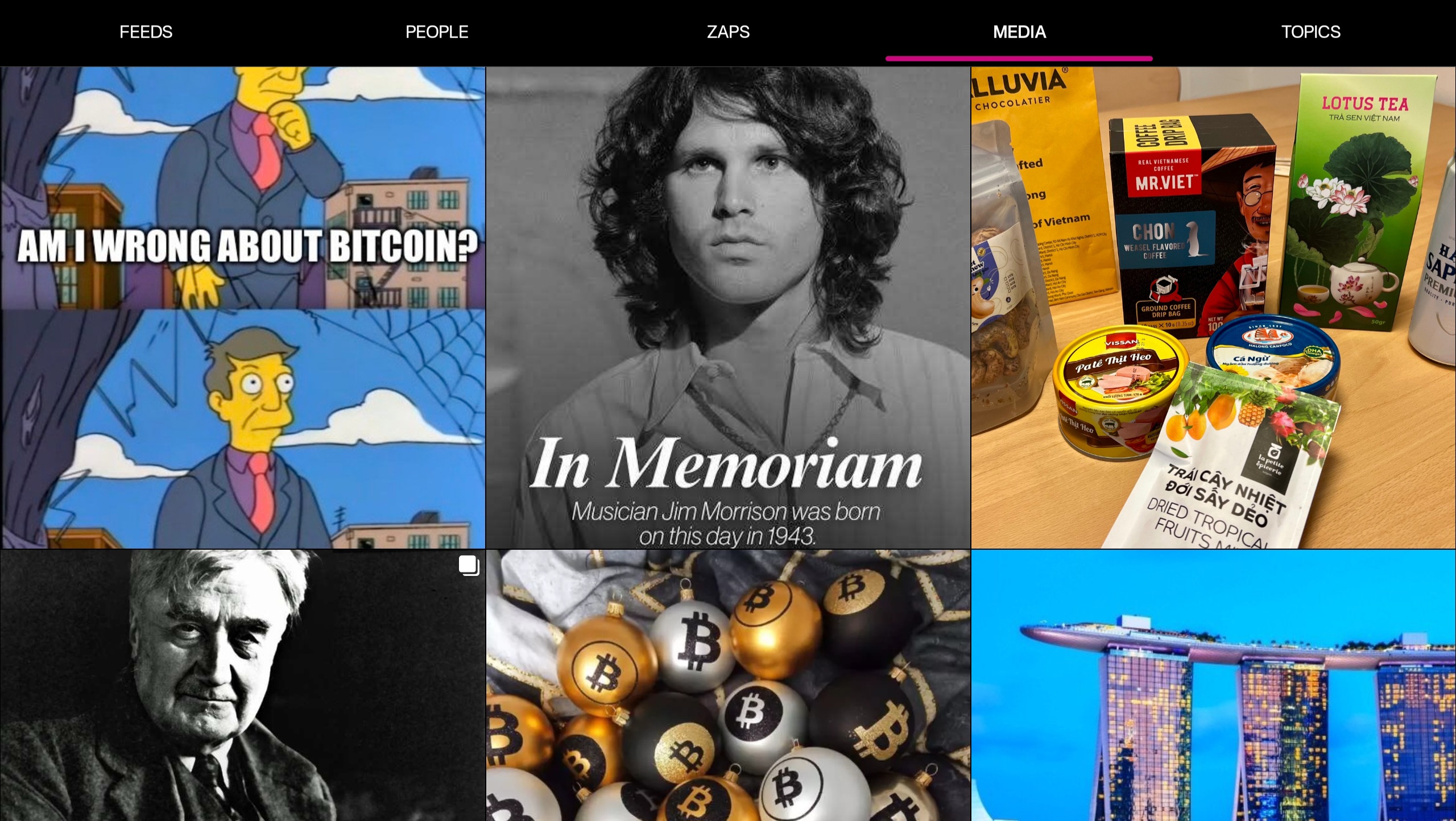
At this point, I would say the web client probably has a bit better UI for use on a tablet than the Android client does, but you miss out on using the built-in wallet, which is a major selling point of the app.
This lack of a landscape mode for tablets and the few very minor UI bugs I encountered are the only reason Primal doesn't get a perfect score in this category, because the client is absolutely stunning otherwise, both in light and dark modes. There are also two color schemes available for each.
Log In Options
Score: 4 / 5 (Updated 4/30/2025)
Unfortunately, Primal has not included any options for log in outside of pasting your private key into the application. While this is a very simple way to log in for new users to understand, it is also the least secure means to log into Nostr applications.
This is because, even with the most trustworthy client developer, giving the application access to your private key always has the potential for that private key to somehow be exposed or leaked, and on Nostr there is currently no way to rotate to a different private key and keep your identity and social graph. If someone gets your key, they are you on Nostr for all intents and purposes.
This is not a situation that users should be willing to tolerate from production-release clients at this point. There are much better log in standards that can and should be implemented if you care about your users.
That said, I am happy to report that external signer support is on the roadmap for Primal, as confirmed below:
nostr:note1n59tc8k5l2v30jxuzghg7dy2ns76ld0hqnn8tkahyywpwp47ms5qst8ehl
No word yet on whether this will be Android signer or remote signer support, or both.
This lack of external signer support is why I absolutely will not use my main npub with Primal for Android. I am happy to use the web client, which supports and encourages logging in with a browser extension, but until the Android client allows users to protect their private key, I cannot recommend it for existing Nostr users.
Update: As of version 2.2.13, all of what I have said above is now obsolete. Primal has added Android signer support, so users can now better protect their nsec by using Amber!
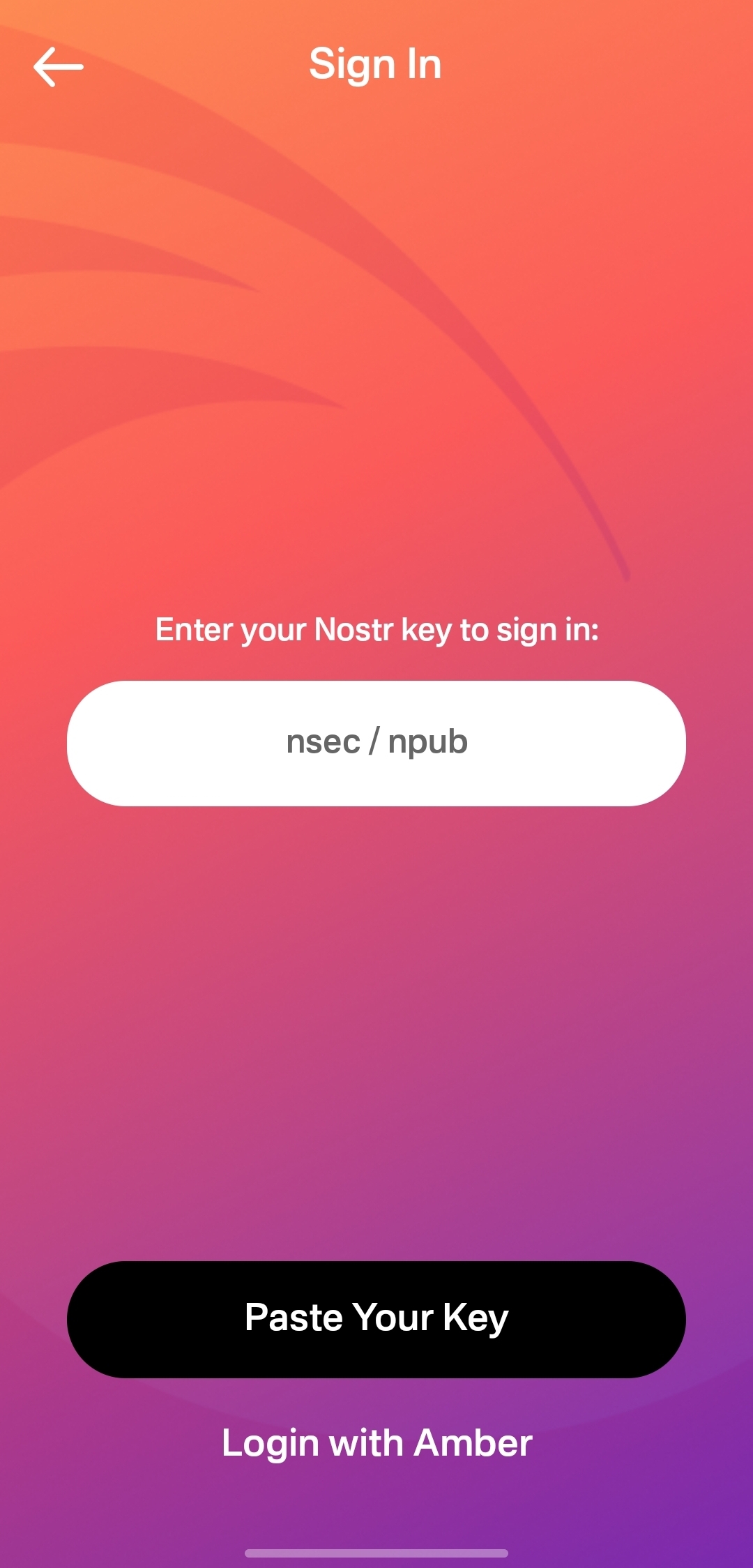
I would still like to see support for remote signers, especially with nstart.me as a recommended Nostr onboarding process and the advent of FROSTR for key management. That said, Android signer support on its own has been a long time coming and is a very welcome addition to the Primal app. Bravo Primal team!
Zap Integration
Score: 4.8 / 5
As mentioned when discussing Primal's built-in wallet feature, zapping in Primal can be the most seamless experience I have ever seen in a Nostr client. Pairing the wallet with the client is absolutely the path forward for Nostr leading the way to Bitcoin adoption.
But what if you already have a Lightning wallet you want to use for zapping? You have a couple options. If it is an Alby wallet or another wallet that supports Nostr Wallet Connect, you can connect it with Primal to use with one-tap zapping.
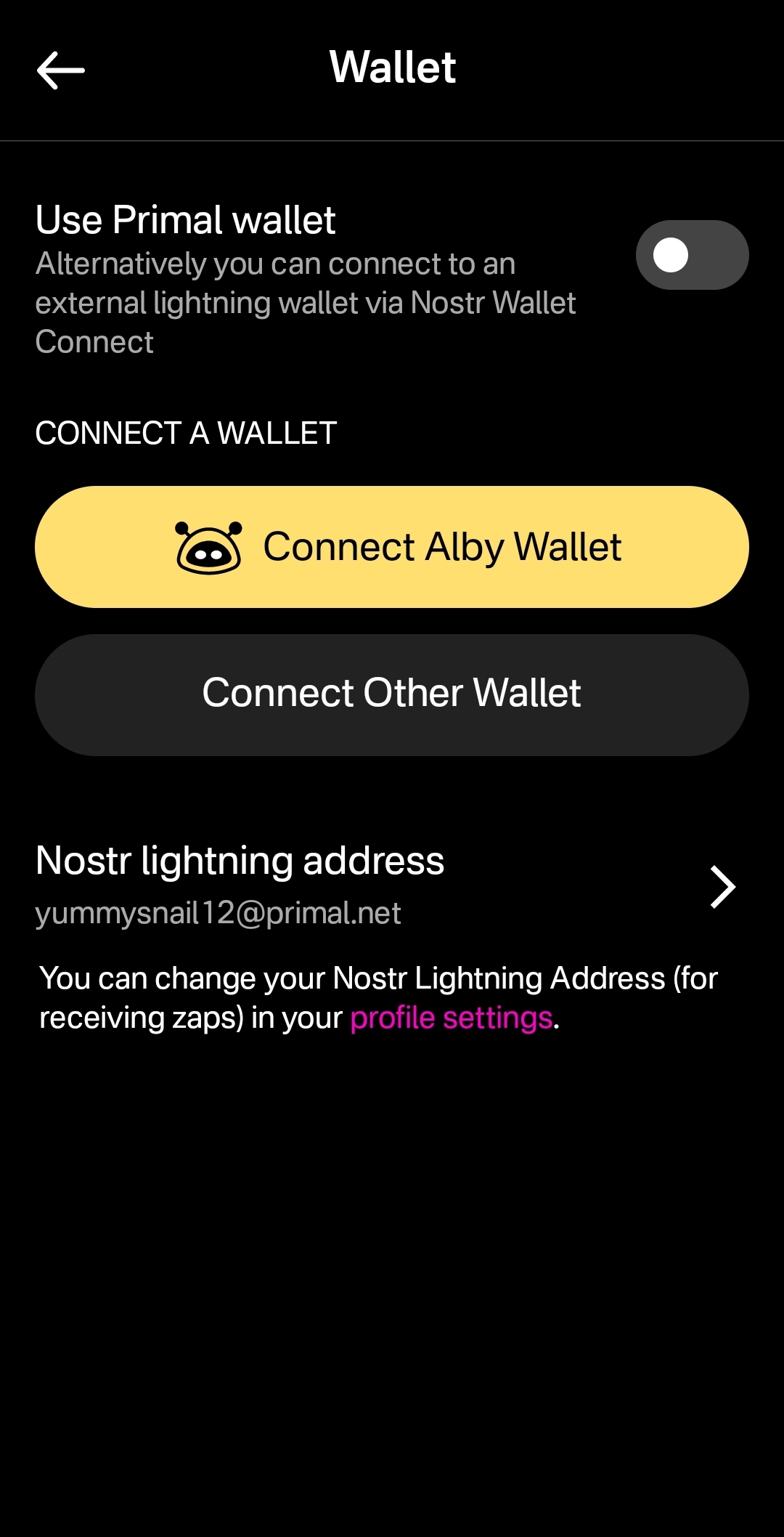
How your zapping experience goes with this option will vary greatly based on your particular wallet of choice and is beyond the scope of this review. I used this option with a hosted wallet on my Alby Hub and it worked perfectly. Primal gives you immediate feedback that you have zapped, even though the transaction usually takes a few seconds to process and appear in your wallet's history.
The one major downside to using an external wallet is the lack of integration with the wallet interface. This interface currently only works with Primal's wallet, and therefore the most prominent tab in the entire app goes unused when you connect an external wallet.
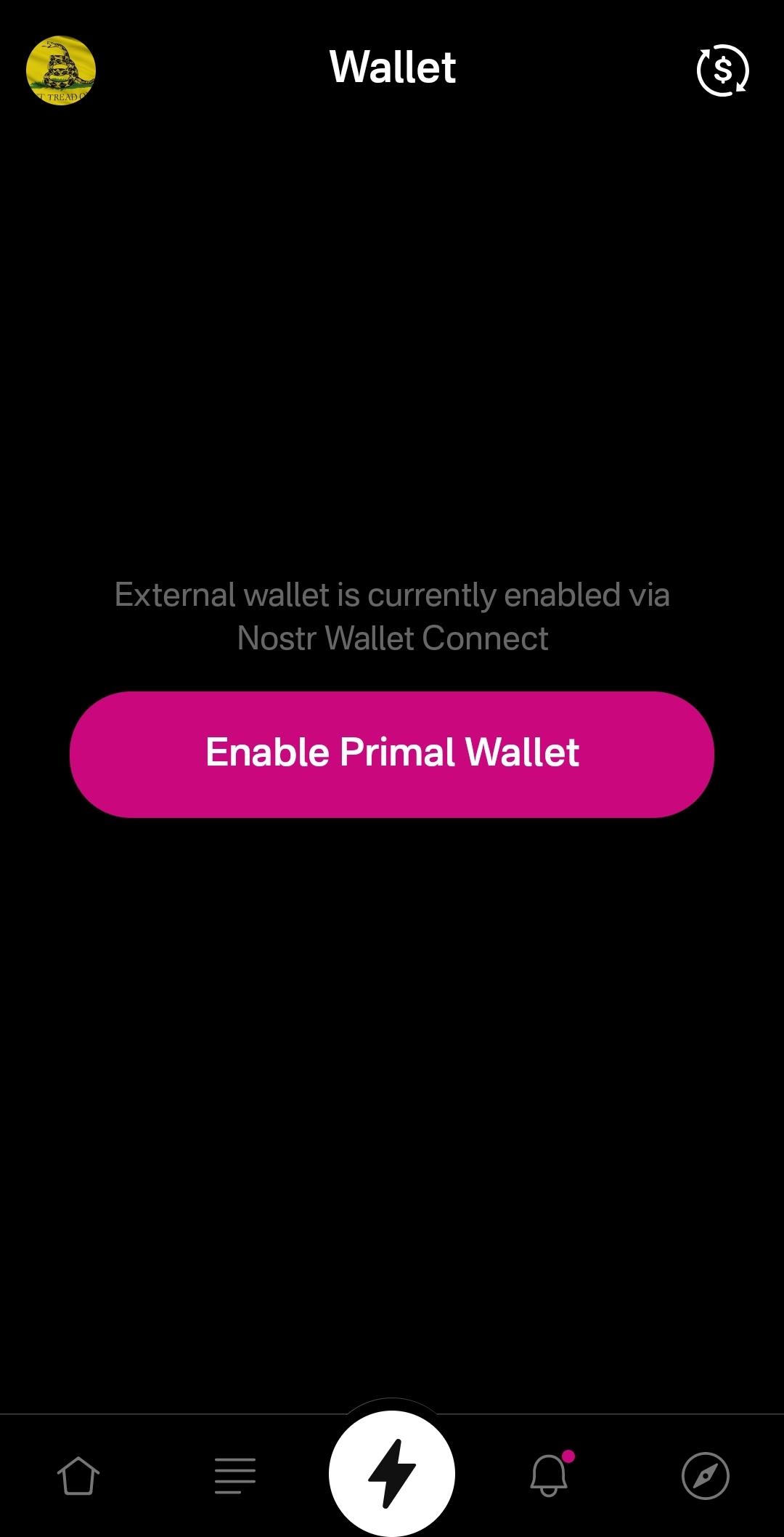
An ideal improvement would be for the wallet screen to work similar to Alby Go when you have an external wallet connected via Nostr Wallet Connect, allowing the user to have Primal act as their primary mobile Lightning wallet. It could have balance and transaction history displayed, and allow sending and receiving, just like the integrated Primal wallet, but remove the ability to purchase sats directly through the app when using an external wallet.
Content Discovery
Score: 4.8 / 5
Primal is the best client to use if you want to discover new content you are interested in. There is no comparison, with only a few caveats.
First, the content must have been posted to Nostr as either a short-form or long-form note. Primal has a limited ability to display other types of content. For instance, discovering video content or streaming content is lacking.
Second, you must be willing to put up with the fact that Primal lacks a means of filtering sensitive content when you are exploring beyond the bounds of your current followers. This may not be an issue for some, but for others it could be a deal-breaker.
Third, it would be preferable for Primal to follow topics you are interested in when you choose them during onboarding, rather than follow specific npubs. Ideally, create a "My Topics" feed that can be edited by selecting your interests in the Topics section of the Explore tab.
Relay Management
Score: 2.5 / 5
For new users who don't want to mess around with managing relays, Primal is fantastic! There are 7 relays selected by default, in addition to Primal's caching service. For most users who aren't familiar with Nostr's protocol archetecture, they probably won't ever have to change their default relays in order to use the client as they would expect.
However, two of these default relays were consistently unreachable during the week that I tested. These were relay.plebes.fans and remnant.cloud. The first relay seems to be an incorrect URL, as I found nosflare.plebes.fans online and with perfect uptime for the last 12 hours on nostr.watch. I was unable to find remnant.cloud on nostr.watch at all. A third relay was intermittent, sometimes online and reachable, and other times unreachable: v1250.planz.io/nostr. If Primal is going to have default relays, they should ideally be reliable and with accurate URLs.
That said, users can add other relays that they prefer, and remove relays that they no longer want to use. They can even set a different caching service to use with the client, rather than using Primal's.
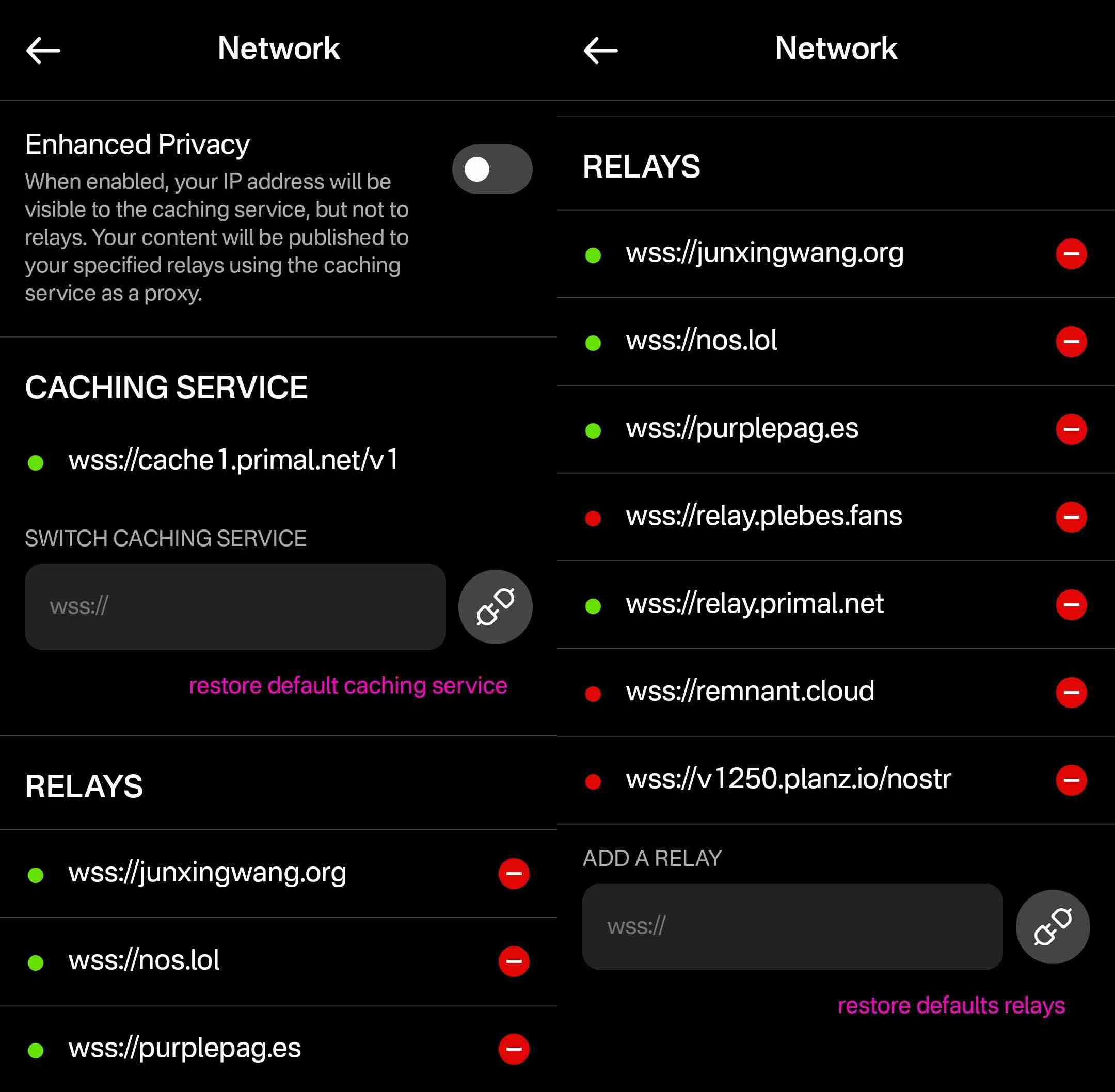
However, that is the extent of a user's control over their relays. They cannot choose which relays they want to write to and which they want to read from, nor can they set any private relays, outbox or inbox relays, or general relays. Loading the npub I used for this review into another client with full relay management support revealed that the relays selected in Primal are being added to both the user's public outbox relays and public inbox relays, but not to any other relay type, which leads me to believe the caching relay is acting as the client's only general relay and search relay.
One unique and welcomed addition is the "Enhanced Privacy" feature, which is off by default, but which can be toggled on. I am not sure why this is not on by default, though. Perhaps someone from the Primal team can enlighten me on that choice.
By default, when you post to Nostr, all of your outbox relays will see your IP address. If you turn on the Enhanced Privacy mode, only Primal's caching service will see your IP address, because it will post your note to the other relays on your behalf. In this way, the caching service acts similar to a VPN for posting to Nostr, as long as you trust Primal not to log or leak your IP address.
In short, if you use any other Nostr clients at all, do not use Primal for managing your relays.
Media Hosting Options
Score: 4.9 / 5 This is a NEW SECTION of this review, as of version 2.2.13!
Primal has recently added support for the Blossom protocol for media hosting, and has added a new section within their settings for "Media Uploads."
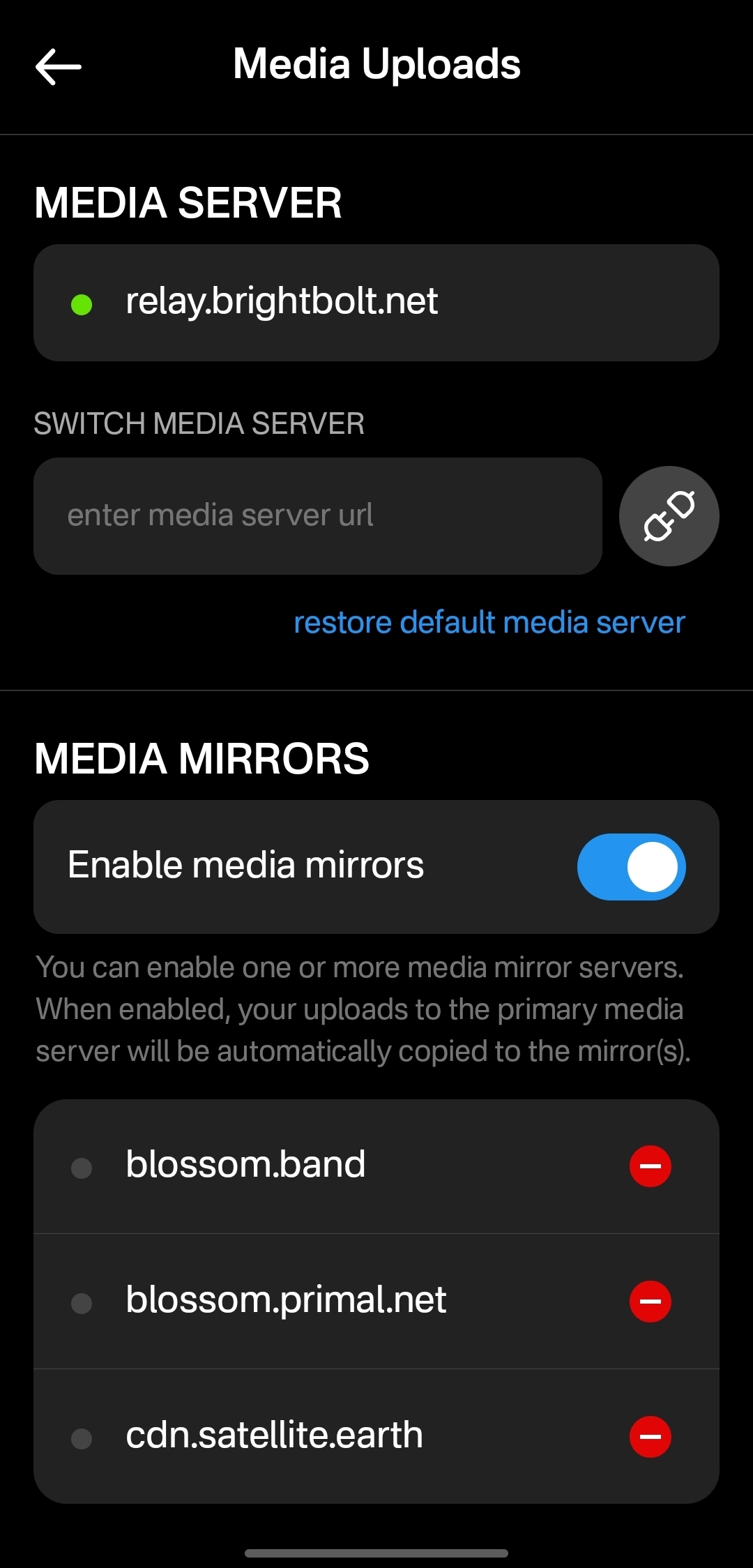
Media hosting is one of the more complicated problems to solve for a decentralized publishing protocol like Nostr. Text-based notes are generally quite small, making them no real burden to store on relays, and a relay can prune old notes as they see fit, knowing that anyone who really cared about those notes has likely archived them elsewhere. Media, on the other hand, can very quickly fill up a server's disk space, and because it is usually addressable via a specific URL, removing it from that location to free up space means it will no longer load for anyone.
Blossom solves this issue by making it easy to run a media server and have the same media mirrored to more than one for redundancy. Since the media is stored with a file name that is a hash of the content itself, if the media is deleted from one server, it can still be found from any other server that has the same file, without any need to update the URL in the Nostr note where it was originally posted.
Prior to this update, Primal only allowed media uploads to their own media server. Now, users can upload to any blossom server, and even choose to have their pictures or videos mirrored additional servers automatically. To my knowledge, no other Nostr client offers this automatic mirroring at the time of upload.
One of my biggest criticisms of Primal was that it had taken a siloed approach by providing a client, a caching relay, a media server, and a wallet all controlled by the same company. The whole point of Nostr is to separate control of all these services to different entities. Now users have more options for separating out their media hosting and their wallet to other providers, at least. I would still like to see other options available for a caching relay, but that relies on someone else being willing to run one, since the software is open for anyone to use. It's just not your average, lightweight relay that any average person can run from home.
Regardless, this update to add custom Blossom servers is a most welcome step in the right direction!
Current Users' Questions
The AskNostr hashtag can be a good indication of the pain points that other users are currently having with a client. Here are some of the most common questions submitted about Primal since the launch of 2.0:
nostr:note1dqv4mwqn7lvpaceg9s7damf932ydv9skv2x99l56ufy3f7q8tkdqpxk0rd
This was a pretty common question, because users expect that they will be able to create the same type of content that they can consume in a particular client. I can understand why this was left out in a mobile client, but perhaps it should be added in the web client.
nostr:note16xnm8a2mmrs7t9pqymwjgd384ynpf098gmemzy49p3572vhwx2mqcqw8xe
This is a more concerning bug, since it appears some users are experiencing their images being replaced with completely different images. I did not experience anything similar in my testing, though.
nostr:note1uhrk30nq0e566kx8ac4qpwrdh0vfaav33rfvckyvlzn04tkuqahsx8e7mr
There hasn't been an answer to this, but I have not been able to find a way. It seems search results will always include replies as well as original notes, so a feed made from the search results will as well. Perhaps a filter can be added to the advanced search to exclude replies? There is already a filter to only show replies, but there is no corresponding filter to only show original notes.
nostr:note1zlnzua28a5v76jwuakyrf7hham56kx9me9la3dnt3fvymcyaq6eqjfmtq6
Since both mobile platforms support the wallet, users expect that they will be able to access it in their web client, too. At this time, they cannot. The only way to have seamless zapping in the web client is to use the Alby extension, but there is not a way to connect it to your Primal wallet via Nostr Wallet Connect either. This means users must have a separate wallet for zapping on the web client if they use the Primal Wallet on mobile.
nostr:note15tf2u9pffy58y9lk27y245ew792raqc7lc22jezxvqj7xrak9ztqu45wep
It seems that Primal is filtering for spam even for profiles you actively follow. Moreover, exactly what the criteria is for being considered spam is currently opaque.
nostr:note1xexnzv0vrmc8svvduurydwmu43w7dftyqmjh4ps98zksr39ln2qswkuced
For those unaware, Blossom is a protocol for hosting media as blobs identified by a hash, allowing them to be located on and displayed from other servers they have been mirrored to when when the target server isn't available. Primal currently runs a Blossom server (blossom.primal.net) so I would expect we see Blossom support in the future.
nostr:note1unugv7s36e2kxl768ykg0qly7czeplp8qnc207k4pj45rexgqv4sue50y6
Currently, Primal on Android only supports uploading photos to your posts. Users must upload any video to some other hosting service and copy/paste a link to the video into their post on Primal. I would not be surprised to see this feature added in the near future, though.
nostr:note10w6538y58dkd9mdrlkfc8ylhnyqutc56ggdw7gk5y7nsp00rdk4q3qgrex
Many Nostr users have more than one npub for various uses. Users would prefer to have a way to quickly switch between accounts than to have to log all the way out and paste their npub for the other account every time they want to use it.
There is good news on this front, though:
nostr:note17xv632yqfz8nx092lj4sxr7drrqfey6e2373ha00qlq8j8qv6jjs36kxlh
Wrap Up
All in all, Primal is an excellent client. It won't be for everyone, but that's one of the strengths of Nostr as a protocol. You can choose to use the client that best fits your own needs, and supplement with other clients and tools as necessary.
There are a couple glaring issues I have with Primal that prevent me from using it on my main npub, but it is also an ever-improving client, that already has me hopeful for those issues to be resolved in a future release.
So, what should I review next? Another Android client, such as #Amethyst or #Voyage? Maybe an "other stuff" app, like #Wavlake or #Fountain? Please leave your suggestions in the comments.
I hope this review was valuable to you! If it was, please consider letting me know just how valuable by zapping me some sats and reposting it out to your follows.
Thank you for reading!
PV 🤙
-
 @ 4961e68d:a2212e1c
2025-05-02 07:46:46
@ 4961e68d:a2212e1c
2025-05-02 07:46:46热死人了!
-
 @ 2ce0697b:1ee3d3fc
2025-04-29 18:54:19
@ 2ce0697b:1ee3d3fc
2025-04-29 18:54:19Excerpt
Special Jurisdictions, Free Cities and Bitcoin Citadels are the sly roundabout way that is removing the market of living together from the hands of the government, without violence and in a way that they can´t stop it. With Bitcoin as the backbone of a new societal order, we are beginning to disrupt the old paradigm.
“If you have built castles in the air, your work need not be lost; that is where they should be. Now put the foundations under them.” ― Henry David Thoreau, Walden
The problem: lack of freedom in the physical realm
Freedom is essential to human life. Being free is what matters. That´s our target, always. No matter the time or space. We pursue freedom because we know its the right thing to do. Freedom is the right to question and change the stablished way of doing things.
Where can we find some freedom? Certainly in the cyberspace. The cyberspace is a free space. Humanity has been blessed by the magic of cryptography, a technology that gave us all the necessary tools to operate in that environment without intervention of undesired third parties.
In cyberspace cryptography performs the function of an impenetrable cyberwall. So, whatever we build in cyberspace can be perfectly protected. Thank to this cybernetic walls we can be sure that the gardens we build and nurture will be protected and cannot be trampled. When we build our digital gardens we have the keys to open the doors to let in whoever we want and most important to leave out whoever we don´t want. In the digital world we can already perfectly interact with one and another in a peer to peer way, without intervention of undesired third parties.
In cyberspace we have Bitcoin for freedom of money and Nostr, torrent and Tor for freedom of information and speech. These open-source protocols are designed to fully realize and expand the promise of freedom, and they certainly deliver what they promise.

So, thanks to the magic of asymmetric cryptography, we´ve already achieved sufficiently descentralization and the possibility of any level of desired digital privacy. Cryptoanarchists and cypherpunks have set their conquering flag in cyberspace and there´s no force on Earth than can remove it. The digital world cannot escape the rules of cryptography. This is great but it only works in the digital realm, meanwhile in the physical realm we are overrun by centralized attackers due to the impossibility of the creation of impenetrable walls such as the ones we have online.
Humans have the upper hand in creating impenetrable walled gardens in cyberspace, but in the physical space authoritarians have the upper hand in bullying physical persons.
The physical world is also naturally free. According to natural law each person is free to do whatever he wants as long as it doesn´t hurt other people. However due to unnatural -artificial and inhuman- centralization of power, the natural freedom of the physical world has been completely undermined. Mostly by Governments, the entities that centralize violence and law.
Bitcoin as a bridge between both realms

Let´s take a look at one connection between both realms, the physical and the digital world. Bitcoin layer one is made essentially of software plus hardware. It consists of any software that produces the same output as the reference implementation - Bitcoin core- and the hardware needed to run that software. Layer two, three or any other layer above, is made essentially of other software and other hardware that interacts with layer one in some way. All these layers, one, two and subsequent, are completely protected by cryptography and a set of game theories that have been successfully tested. Each new block added to the timechain is a testimony of the unstoppable force of freedom and meritocracy.
Before layer one we have Bitcoin layer zero, which is essentially the sum of all actions and inactions done by bitcoiners regarding to or because of bitcoin. In other words, layer zero is composed by flesh and bone people interacting in some way with layer one of the bitcoin network.
Hence, an attack on a bitcoiner - on his way of life- is an attack on bitcoin, the network itself. First because it is an attack on a layer zero node, the physical person, the bitcoiner under duress or coercion. And second because is also an attack on the store-of-value-aspect of bitcoin. Nowaday, the most common attack against bitcoiners is the entirety of compliance regulations. This is the sum of all coercive regulations,such as laws, threats of more laws, imprisonment, threats of more imprisonment, taxation, threats of more taxation, requirements to prove the origin of funds, coercive removal of privacy such as the travel rule, unnecessary bureaucracy such as the need to obtain a money transmitting license and many others rules, in a never stopping inflationary coercive legislation.

If a physical attack is preventing any bitcoiner to exchange the value he created for bitcoin due to any kind of artificial obstacles -such as any kind of compliance- that specific attack is successful in the sense that even though the whole network keeps operating, the attack itself diminishes the value of all the bitcoins.
So, even if layer-zero cannot be taken down, every interference on this layer is an attack on the bitcoin network. Attacks on layer one, two or any other layer that exists in the cyberspace can interfere with the network but they may hardly subtract any value from it. For example we have already been through plenty of times where hashing power was diminished due to government intervention and the bitcoin network remain completely unaffected.
On the other hand successful attacks on layer zero subtract potential, but real and demonstrable value. This value is equal to the amount of value the frustrated user would have added to the network if he would have been able to use it freely, that means if he would have sold his product without the cost of compliance. I´ll demonstrate this in the next chapter.
The cost of compliance
Alice is a merchant specialized in a specific area and topic. She studied the market, her business, her suppliers, consumers, the logistics involved, marketing, design, and everything necessary to become a successful entrepreneur. After investing a considerable amount of resources, she developed a perfect product. Or at least she considers it perfect, that is, the best in its class. While developing everything necessary to create her product, she met Bob, who became her main lead and stereotype of a buyer persona. She knows what Bob wants and she wants to sell it to him. According to Alice's calculations, for her business to be viable, she must sell the product at ten satoshis per unit, and fortunately, Bob is willing to pay that price for it. Alice's product is finished, ready to hit the market, but just before sending it to production, Alice decides to take a pause to analyze her reality. Before taking the public action of making her product available in the open market, Alice analyzes her material, political, and legal reality. In doing so, she realizes that she lives under the jurisdiction of a State. She learns that the Government prescribes through its regulations how she must behave. She analyzes that in order to sell her product legally, in compliance, she must make a series of modifications to it. The product before hitting the shelves must first be modified both in the way it is presented to the market and also regarding certain technical characteristics that it possesses. She must also modify the way it produces her product by changing the contractual relationship with its suppliers, distribution channels, and all other types of logistics involved. She must make all these changes even if they bring about significant and insurmountable inefficiencies.
Likewise, Alice also sees that she not only has to modify the product but also has to meet tax obligations. In addition to paying an accountant since the tax obligations by some irrational reason are not calculated by the creditor. Additionally, she must hire other professionals to assist her in studying the current regulations and how they should be applied in all stages of production, distribution, and sale of her product.
Alice, being a rational person, wishes to avoid having to make these modifications since they increase her costs while also decreasing the quality of her product. But when studying compliance, that is, the entirety of applicable regulations, she also examines the consequences of not being in compliance. Alice realizes that if she does not comply with the regulations, she risks having all her assets legally confiscated, going to prison, being killed while they try to capture her to imprison her, and, if she goes to prison, being tortured in jail by other inmates or by State officials in charge of holding her in that place. So, since Alice does not want to suffer these negative consequences, she decides to modify the product and be in compliance.
So, Alice makes the necessary changes and puts her new version of the product on the market. Then she has the following dialogue with Bob, her lead, the interested party in acquiring the product.
Bob: - Hey Alice, nice meeting you here in this market. I came to buy the product you were developing and told me about. However, this product I´m seeing now is not what you promised me. This is clearly inferior.
Alice: - Yeah, I know. I'm sorry Bob, but I prefer to sell this inferior product rather than risk having all my assets confiscated, going to prison, being killed while they try to capture me, and if they don´t kill but managed to put me in jail I could be tortured there.
Bob: - Ok, no problem. Thats quite understandable. I don´t believe anyone would prefer those kind of experiences. But given the quality of the product, I no longer intend to pay you ten satoshis; I only offer you eight. Shall we close the deal?
Alice: - I'm sorry Bob, but I can't sell it to you for eight sats. Due to government intervention and its requirements, now I can't even sell it for less than thirteen satoshis.
Bob: - Ok. Considering this I prefer not to purchase it. I will keep looking for alternatives. Bye

Some time later, Charlie arrives at the market, who is also interested in the product and, despite it not being like the original version, decides to purchase it by paying the thirteen satoshis demanded by the seller Alice.
Meanwhile, in the same universe, we have Daniel, the last character in this example. Daniel is a merchant competing with Alice. Daniel has a product that is very similar, practically identical to the one originally designed by Alice. Like Alice, Daniel initially also wants to sell it for ten satoshis. Just like Alice, before heading to the market, Daniel analyzes the reality in which he lives. And it turns out that he also lives under the jurisdiction of a State. Daniel too then analyzes the entirety of the applicable regulations and also comes to the conclusion that to comply with them, he would also need to modify the product and cover all the additional expenses artificially generated to be in compliance.
However, Daniel's ethics are different from Alice's. Daniel understands that his product is indeed perfect (the best in its class) and that therefore modifying it would go against its essence. Daniel understands that changing the product would be a betrayal of his creation and therefore a betrayal of his own self and the essence of his being. Daniel conducts an ethical analysis of his actions and the moral implications of putting the product on the market. Daniel sees that the product not only does not harm anyone but is also made to be freely acquired by adults who give their consent for its purchase and subsequent use. Daniel also understands that paying taxes only serves to promote the slavery system driven by fiat and that whenever he can avoid collaborating with the immoral fiat system, it is his ethical obligation to do so. Likewise, Daniel highlights the hypocrisy and inefficiencies of anti-money laundering regulations, as well as the futility of requiring licenses for naturally free acts that do not harm others. For all these reasons, Daniel decides to sell the product in its current state irregardles of compliance regulations.
However, before going to market, Daniel also studies the possible consequences of neglecting compliance. By doing so, Daniel sees that if he does not comply with the regulations, he risks having all his assets legally confiscated, going to prison, being killed while they attempt to capture him to imprison him, and, in the event of going to prison, being tortured in jail by other inmates or by State officials responsible for holding him in that place. So, since Daniel is a rational person who does not want to suffer these negative consequences but also does not want to betray his product and himself, he decides to take the risk of not being in compliance. After making this decision, Daniel puts the product on the market and there he meets Bob. In doing so, they converse in the following terms:
Bob: - Hey Daniel, this product is exactly what I was looking for. A product like the one promised by Alice but never delivered. I love it! I offer you ten satoshis for it.
Daniel: - Thank you for your feedback Bob and for the offer! However I am currently selling it for eleven satoshis. Ten satoshis seems like a good price to me, and it was indeed my original intention to sell it for that amount because at that price I achieve competitiveness and a sustainable business model.
Bob: - So why are you asking me for eleven satoshis? Interrupts Bob
Daniel: - Because that price is calculated before assessing compliance and the risks associated with non-compliance. By not complying with the regulation, I managed to maintain the quality of the product and avoided a large amount of unnecessary expenses, but there is no way to avoid the risk of facing penalties for non-compliance. To bring this product to market, I had to incur several expenses in order to minimize the risk of non-compliance as much as possible. While I am taking all reasonable actions to prevent all of my assets from being legally confiscated, from going to prison, from being killed while they try to capture me, and in case of going to prison, from being tortured, the reality is that I still run the risk of all that, or part of all that, happening to me, my family, or any of my company's employees. The remaining risk balance is transferred to the price along with the costs of mitigating those risks. The total of those costs and the remaining risk I estimate them at one satoshi per unit of product. Therefore, I can't sell you the product for ten satoshis, but I can sell it to you for eleven.
To which Bob, lacking a better option in the market, ends up buying the product for eleven satoshis.
In summary: two products were made by two different merchants whose business model allowed them, in both cases, to put the product on the market at a rate of ten satoshis per unit. However, in one case, a lower quality product was sold for thirteen satoshis, and in the other case, a higher quality product was sold for eleven satoshis. That is to say, in the first case there was an overprice or inefficiency objectively measured at three satoshis, while in the second case there was an overprice or inefficiency of one satoshi. So, we are facing a total loss of value equivalent to four satoshis. The value represented by these four satoshis was absorbed by the inefficiency programmed and ruled by the State. The example shows us that whether one chooses the compliance route, as Alice did, or the free market route, as Daniel did, in both cases the existence of regulations generates an additional cost to the market. In this example the state attack on layer zero was successful and extracted from the Bitcoin network a value of four satoshis.
Bitcoin is money
Bitcoin is many things but essentially is money. And money sole purpose is to store value in order to facilitate future exchanges of products and services with other people. Without the products and services to be exchanged for the money, money itself would be useless and worthless. We only use money because we may require favors, benefits, services, products from other people in the future. And we don´t know which services and products we´ll need nor exactly when we are goint to need them.

The total value of bitcoin equals to infinity divided twenty one millions. This is because the total worth of the network mirrors the total worth of accumulated capital by the entirety of mankind throughout its entire history. That is clearly a lot of value. But if the if the dividend equals zero then the divisor is also zero and if the dividend growth is obstructed through artificial means -such as compliance- then the divisor growth is also obstructed.
Bitcoin layer zero, the bitcoiners and the services and products we create, are what give value to the twenty one million units of bitcoin.
Freedom is without a doubt the best context for value creation. So, the more and better games we can create that allow humankind to find a way to exercise freedom, then the most value we can add to all the layers of the network.
This is why the most important layer of the whole bitcoin phenomenon is layer zero, the bitcoiners. Hence the problem to be solved is not how to prevent bitcoin - layer one upwards- from successful attacks. The problem to solve is how to prevent attacks on layer zero. Or in other words, the problem to be solved is how to get bitcoiners in the physical world to practice the same level of freedom that bitcoin achieves in the cyberspace.
Summary of the first part of this article: freedom in cyberspace has already been conquered and each further development in the digital realm contributes to further developments but only in the same realm. Meanwhile in the physical space, the layer zero of bitcoin is under constant attacks that successfully extract value from it.
Exercising freedom in a sly roundabout way

In 1984 the Austrian economist Friedrich Hayek predicted that we couldn´t take money with violence out of the hands of government. He stated that we needed to do it in a sly roundabout way. Twenty five years later Satoshi Nakamoto discovered the sly roundabout way actually introducing something that the government couldn´t stop. Thus fulfilling Hayek´s prophecy.
Bitcoin is a sly roundabout way that removed money without violence from the hands of the government in a way that they can´t stop it.
Cryptography in general and protocols such as Tor and Tails are a sly roundabout way that removed confidential information from the hands of the government without violence in a way that they can´t stop it.
Nostr is a sly roundabout way that removed social media and public information from the hands of the government without violence in a way that they can´t stop it.
Special Jurisdictions, Free Cities and Bitcoin Citadels are the sly roundabout way that is removing the market of living together from the hands of the government without violence in a way that they can´t stop it.

So, what are Special Jurisdictions, Free Cities and Bitcoin Citadels? To understand what they are we can take a look at the current mainstream market of living together, at how the physical space is organized. Essentially the entire planet Earth and its surroundings are run by a conglomerate of Governments. They create all the rules, regarding every aspect of life, of all the individuals, and enforce every rule through coercive means.
In the mainstream market of living together individuals have several alternatives to pick from. We can choose to live in a natural city or a pre design city, in a public neighborhood or private neighborhood or even in an intentional community with common interest amongst the users. But irregardless of the choice, every product offered in the mainstream market has the sames rules which are established by the host state to the entirety of organizations in his territory. In the mainstream market, even the most different products abide by the same high level rules such as criminal law, civil law, taxation laws, customs, enviromental laws, money laundering regulations and many others. To abide to the sum of all the laws and regulations is to be in compliance.
The centralization of regulations makes extremely difficult to experiment in market of living together. The less experimentation is allowed, the more human progress is hindered.
So what is the sly roundabout that fixes this? What are Special Jurisdictions, Free Cities and Bitcoin Citadels? I´m using the term Special Jurisdictions as an umbrella term that includes the entire spectrum of iterations of products that aim to modify the mainstream rules of the market of living together.
This term includes all the different models such as Charter Cities, Free Cities, Special Economic Zones, microstates, micropolis, start up societies, government as a service, self governing jurisdictions, autonomous intentional communities, network states and Bitcoin Citadels. The array of possible iterations is huge and permanently expanding. What they all have in common is that each of these experiments aims to create a functional game theory that replaces the lack of unbreakable walls in the physical space.
Let´s take a look of a couple of examples. Special Economic Zones are bounded areas of countries that have their own rules and regulations. Worldwide, there are more than five thousands special economic zones located in more than hundred countries.
One of them is the special economic zone of Shenzhen in China. The Chinese government allowed Shenzhen the freedom to experiment with certain practices that were prohibited in the rest of the country at the time. This included allowing foreign companies to make direct investments in China, allowing people to buy and sell land, allowing Chinese people to set up their own private businesses and relaxation of the system that limited internal migration within China for Chinese citizens. It served as a place where China could experiment with market reforms. The experiment was such a huge economic success that it was replicated in many other areas of the country.
Another place that has made extensive use of special economic zones is Dubai. The monarchic Government has more than 30 SEZs. In this case one of the many obstacles removed by the host state its the monopoly of the legal system. Dubai Government allowed the special economic zone to have its own independent legal system thus conceding a modification of the mainstream rules in that area.
This kind of projects, such as Dubai or Shenzhen, are a top-to-down product. Fully created by the Governments thus compliant with their own regulations.

On the other side of the spectrum we have Citadels and several other archetypes of not so compliant projects .
For example the Free Commune of Penadexo it´s a grassroots project building a freedom-oriented community in one of Spain’s abandoned villages.
 It´s model is based on building a peer to peer society avoiding government intervention as much as possible.
They stablished themselves in an abandoned historic village and the started to track down the owners to purchase as much property as possible. Meanwhile, they are living there and expanding their users base while also reconstructing buildings.
It´s model is based on building a peer to peer society avoiding government intervention as much as possible.
They stablished themselves in an abandoned historic village and the started to track down the owners to purchase as much property as possible. Meanwhile, they are living there and expanding their users base while also reconstructing buildings. This is an example of a completely different way of dealing with the Government. While Special Economic Zones are fully compliant and created top to down, this model on the other hand is bottom-up and aims to add value to the users relying in factual freedom which is exercised by stablishing the commune away from heavily populated centers where Government grip is tighter. Under this model the interaction with the Government is kept as low as possible. Their strategy relies in ignoring the Government as much as possible and being a good neighbor. With this simple and effective tactic some Citadels enjoy the benefits of liberty in their lifetime without needing to spend huge resources in governmental lobby.
There are countless models or archetypes of Bitcoin Citadels trying to solve the obstacles in different ways, trying to restart the system. And one of the challenges of the Bitcoin Citadels is how to connect the different projects to boost and help each other.
This is where The Meshtadel comes into play. The Meshtadel is a system where decentralized tactics are used to help and defend citadels connected in a global network. With real life connections with fellow bitcoiners. Its an organization equivalent to the hanseatic league built under a starfish model. If you cut off a spider’s head, it dies, but if you cut off a starfish’s arm, it can regenerate and even grow into a new starfish.
The Meshtadel its a network of peer relationships, with ambiguous leadership roles, trust among participants, a shared ideology and vision based on the Bitcoin ethos, and an open system where new nodes - bitcoin citadel builders - can participate.
The long term goal of the Bitcoin Meshtadel is to help Bitcoin Citadels to gain the support of a critical mass of the total population. If enough people see that Bitcoin is as peaceful as it gets, in the long run, some nations could become friendly and supportive enough to legally tolerate the Bitcoin Citadel inside its territory in the form of a Bitcoin safe haven. In the Meshtadel we are fighting from the moral high ground using memes, Nostr notes and zapping our way into freedom creating an online and offline circular economy.
TO CONCLUDE:
Special Jurisdictions, Free Cities and Bitcoin Citadels are the sly roundabout way that is removing the market of living together from the hands of the government, without violence and in a way that they can´t stop it.
Nation states, abusing the myth of authority, have halted development on the market of living together for so long that a blooming freer market is eating its lunch. The sovereign individual thesis is live and continuously expanding. The network state is forming and intentional communities are flourishing all around the world reshaping globally the relationship between individuals and the governments.
With global internet connections, uncensorable means of communication and Bitcoin as the backbone of a new societal order, we are beginning to disrupt the old paradigm.
The fashion of the present world is passing away, let’s help it to move forward along by building Special Jurisdictions, Free Cities and Bitcoin Citadels.
--- --- --- --- --- --- --- --- ------
byCamiloat 875.341 timechain.
If you find this content helpful, zap it to support more content of the sort and to boost the V4V model.
-
 @ 266815e0:6cd408a5
2025-04-29 17:47:57
@ 266815e0:6cd408a5
2025-04-29 17:47:57I'm excited to announce the release of Applesauce v1.0.0! There are a few breaking changes and a lot of improvements and new features across all packages. Each package has been updated to 1.0.0, marking a stable API for developers to build upon.
Applesauce core changes
There was a change in the
applesauce-corepackage in theQueryStore.The
Queryinterface has been converted to a method instead of an object withkeyandrunfields.A bunch of new helper methods and queries were added, checkout the changelog for a full list.
Applesauce Relay
There is a new
applesauce-relaypackage that provides a simple RxJS based api for connecting to relays and publishing events.Documentation: applesauce-relay
Features:
- A simple API for subscribing or publishing to a single relay or a group of relays
- No
connectorclosemethods, connections are managed automatically by rxjs - NIP-11
auth_requiredsupport - Support for NIP-42 authentication
- Prebuilt or custom re-connection back-off
- Keep-alive timeout (default 30s)
- Client-side Negentropy sync support
Example Usage: Single relay
```typescript import { Relay } from "applesauce-relay";
// Connect to a relay const relay = new Relay("wss://relay.example.com");
// Create a REQ and subscribe to it relay .req({ kinds: [1], limit: 10, }) .subscribe((response) => { if (response === "EOSE") { console.log("End of stored events"); } else { console.log("Received event:", response); } }); ```
Example Usage: Relay pool
```typescript import { Relay, RelayPool } from "applesauce-relay";
// Create a pool with a custom relay const pool = new RelayPool();
// Create a REQ and subscribe to it pool .req(["wss://relay.damus.io", "wss://relay.snort.social"], { kinds: [1], limit: 10, }) .subscribe((response) => { if (response === "EOSE") { console.log("End of stored events on all relays"); } else { console.log("Received event:", response); } }); ```
Applesauce actions
Another new package is the
applesauce-actionspackage. This package provides a set of async operations for common Nostr actions.Actions are run against the events in the
EventStoreand use theEventFactoryto create new events to publish.Documentation: applesauce-actions
Example Usage:
```typescript import { ActionHub } from "applesauce-actions";
// An EventStore and EventFactory are required to use the ActionHub import { eventStore } from "./stores.ts"; import { eventFactory } from "./factories.ts";
// Custom publish logic const publish = async (event: NostrEvent) => { console.log("Publishing", event); await app.relayPool.publish(event, app.defaultRelays); };
// The
publishmethod is optional for the asyncrunmethod to work const hub = new ActionHub(eventStore, eventFactory, publish); ```Once an
ActionsHubis created, you can use therunorexecmethods to execute actions:```typescript import { FollowUser, MuteUser } from "applesauce-actions/actions";
// Follow fiatjaf await hub.run( FollowUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d", );
// Or use the
execmethod with a custom publish method await hub .exec( MuteUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d", ) .forEach((event) => { // NOTE: Don't publish this event because we never want to mute fiatjaf // pool.publish(['wss://pyramid.fiatjaf.com/'], event) }); ```There are a log more actions including some for working with NIP-51 lists (private and public), you can find them in the reference
Applesauce loaders
The
applesauce-loaderspackage has been updated to support any relay connection libraries and not justrx-nostr.Before:
```typescript import { ReplaceableLoader } from "applesauce-loaders"; import { createRxNostr } from "rx-nostr";
// Create a new rx-nostr instance const rxNostr = createRxNostr();
// Create a new replaceable loader const replaceableLoader = new ReplaceableLoader(rxNostr); ```
After:
```typescript
import { Observable } from "rxjs"; import { ReplaceableLoader, NostrRequest } from "applesauce-loaders"; import { SimplePool } from "nostr-tools";
// Create a new nostr-tools pool const pool = new SimplePool();
// Create a method that subscribes using nostr-tools and returns an observable function nostrRequest: NostrRequest = (relays, filters, id) => { return new Observable((subscriber) => { const sub = pool.subscribe(relays, filters, { onevent: (event) => { subscriber.next(event); }, onclose: () => subscriber.complete(), oneose: () => subscriber.complete(), });
return () => sub.close();}); };
// Create a new replaceable loader const replaceableLoader = new ReplaceableLoader(nostrRequest); ```
Of course you can still use rx-nostr if you want:
```typescript import { createRxNostr } from "rx-nostr";
// Create a new rx-nostr instance const rxNostr = createRxNostr();
// Create a method that subscribes using rx-nostr and returns an observable function nostrRequest( relays: string[], filters: Filter[], id?: string, ): Observable
{ // Create a new oneshot request so it will complete when EOSE is received const req = createRxOneshotReq({ filters, rxReqId: id }); return rxNostr .use(req, { on: { relays } }) .pipe(map((packet) => packet.event)); } // Create a new replaceable loader const replaceableLoader = new ReplaceableLoader(nostrRequest); ```
There where a few more changes, check out the changelog
Applesauce wallet
Its far from complete, but there is a new
applesauce-walletpackage that provides a actions and queries for working with NIP-60 wallets.Documentation: applesauce-wallet
Example Usage:
```typescript import { CreateWallet, UnlockWallet } from "applesauce-wallet/actions";
// Create a new NIP-60 wallet await hub.run(CreateWallet, ["wss://mint.example.com"], privateKey);
// Unlock wallet and associated tokens/history await hub.run(UnlockWallet, { tokens: true, history: true }); ```
-
 @ 57d1a264:69f1fee1
2025-05-02 06:17:05
@ 57d1a264:69f1fee1
2025-05-02 06:17:05Simple design
For as long as I remember, I’ve believed in simple design as a principle in my practice. It feels fundamental to me when I think about good design.
At the same time, I see many successful examples of complex products in the world. So I decided to ask, what value is simple design really providing me and my work?
Is it nostalgia?
I sometimes wonder if simple design is rooted in nostalgia. An example I like to use is:
Imagine yourself in the year 1981. You just purchased a brand new desk calculator. You are excited because you should be able to do any type of paperwork calculations you can imagine on it.
As you start to use it for the first time, it immediately prompts you to update its software. After using it for a few calculations, it asks you to fill out a survey about your experience. One day in the middle of adding up your checkbook, it interrupts you to tell you about a new leather-bound desk calendar the company just released. Sometimes in the middle of a complex calculation, the calculator will lag and crash. You have to restart it often to fix the issue.
I have a feeling that a person in 1981 would think this is a terrible calculator. They purchased the device to perform their calculations, nothing more. Why is it requiring so much more of their attention and effort?
Focus
I think simple design often refers to a focused product. A product that does a specific task can sometimes do that task really well. Products that try to do many things can offer a lot of value, but rarely do all the things well.
Some people prefer to use specific tools for specific tasks. Others prefer a wide variety of features.
I think the benefits of using fewer products are often a major reason complex products are successful. They may not be focused, they might be lower quality as a result, but people can use them for a wide variety of applications.
You can open a can of beans with a Swiss Army Knife — it will get the job done.
Art and subjectivity
Maybe simple design is valuable for intangible reasons. There is an art to simplicity. There is a beauty to simplicity.
A user can see more of the product's intentionality. The creator chose to leave certain features out. They decided what to include. The product likely exudes more vision and personality.
That might be unnoticed by some, but very valuable to others who care about craft. People who value the experience as much as the result.
Ease of use
I think a true benefit of simple design is the effect it has on ease of use. The less things there are to do in a product, the more obvious the things you can do become.
A simple product requires less of a user. That means a user can stay focused on their own needs and use the product in ways they define. They will encounter boundaries which limit them. These limitations could drive some away, but some might be engaged to find new and creative ways of working.
When to abandon simple design
I think the sad news is simple design is ultimately a limiting factor of a product's growth. I think there are many examples of this throughout the course of history (i.e. Ello vs Facebook, Rdio vs Spotify, Simplenote vs Notion, VSCO vs Instagram, Clear vs Things, Peach vs Twitter, etc). At the same time, I think 'simple design' does provide an entry point to successfully define what a product is.
The biggest challenge is continuing to evoke the benefits of simple design in an established product, while allowing a product to evolve and grow to meet its users' needs. That is a balancing act that very few products have ever achieved, but feels like an ideal that successful products should strive for.
One of Charlie Deets Writings
originally posted at https://stacker.news/items/969089
-
 @ 57d1a264:69f1fee1
2025-05-02 06:04:19
@ 57d1a264:69f1fee1
2025-05-02 06:04:19After being featured in the NY Times and WSJ, New York City officially opens a major addition to Central Park, the Davis Center at the Harlem Meer. Designed by architect Susan T Rodriguez in collaboration with Mitchell Giurgola, the renovation project replaces the old Lasker Rink and pool with a recreational facility that’s built directly into the landscape, restoring nature, reconnecting paths, and creating a year-round space for community activity. At the heart of the new design is a transformative water feature that shifts with the seasons, from a skating rink in winter to a lush green lawn in spring and fall and a pool in the summer.
The center’s new oval-shaped pool sits lower than the old one, surrounded by a gently sloped grassy berm. In winter, the pool becomes an ice-skating rink, making the site a destination in every season. A splash pad at the end of the water feature offers extra water play in the summer. By integrating the design into the natural shape of the land, the architects were able to open up the space around the pool and allow the landscape to flow around it, resulting in a setting that feels like it’s always been there.
Sustainability was a core part of the project. The building is expected to earn LEED Gold certification, thanks to features like passive ventilation, locally sourced stone and wood, energy-efficient systems, and a roof that absorbs rainwater. Bird-safe glass helps protect local wildlife, and recycled materials from the old building were reused during construction. Even more important, the new center supports free and low-cost programming year-round, including education, nature walks, community events, and recreation. It’s designed to welcome all kinds of visitors—from families and school groups to joggers, birdwatchers, and casual parkgoers.
Continue reading: https://www.designboom.com/architecture/giant-pool-new-york-central-park-new-davis-center-susan-t-rodriguez-mitchell-giurgola-04-24-2025/
originally posted at https://stacker.news/items/969086
-
 @ 57d1a264:69f1fee1
2025-05-02 05:16:39
@ 57d1a264:69f1fee1
2025-05-02 05:16:39Large Language Models (LLMs) have transformed software engineering, but their application to physical engineering domains remains underexplored. This paper evaluates LLMs' capabilities in high-powered rocketry design through RocketBench, a benchmark connecting LLMs to high-fidelity rocket simulations. We test models on two increasingly complex design tasks: target altitude optimization and precision landing challenges. Our findings reveal that while state-of-the-art LLMs demonstrate strong baseline engineering knowledge, they struggle to iterate on their designs when given simulation results and ultimately plateau below human performance levels. However, when enhanced with reinforcement learning (RL), we show that a 7B parameter model outperforms both SoTA foundation models and human experts. This research demonstrates that RL-trained LLMs can serve as effective tools for complex engineering optimization, potentially transforming engineering domains beyond software development.
PDF: https://arxiv.org/pdf/2504.19394
Source: https://arxiv.org/abs/2504.19394
originally posted at https://stacker.news/items/969083
-
 @ 318ebaba:9a262eae
2025-05-02 04:57:05
@ 318ebaba:9a262eae
2025-05-02 04:57:05Dies ist ein Test
-
 @ 3ffac3a6:2d656657
2025-05-02 03:50:51
@ 3ffac3a6:2d656657
2025-05-02 03:50:51Introduction: Don't Despair—This Can Be Fixed (But Don't Reboot Yet)
Running ZFS on a Raspberry Pi offers powerful features for home servers and personal NAS setups. But with power comes complexity, and in recent months, a quiet pitfall has emerged for Pi users who track kernel updates closely: upgrading to an unsupported kernel version breaks ZFS.
⚠️ Important Warning: If you've just upgraded your kernel and you're using ZFS, do not reboot yet. Rebooting without a working ZFS module can leave your system unbootable—even if you don't have critical partitions on ZFS. The system may hang because it tries to load the missing ZFS kernel module during boot and fails, halting the boot process.
If you're already facing a broken setup or can't boot — don't panic. This guide outlines both the worst-case scenario and the ideal recovery strategy. Whether you're locked out or preparing for a smooth upgrade, we've got you covered.
The Problem: A Kernel Update Too Far
As of ZFS version 2.2.3 (used in Debian-based Raspberry Pi OS), the filesystem supports Linux kernels up to 6.7. However, Raspberry Pi OS backports recently began shipping 6.12.x kernels. If you upgrade to 6.12 without precautions:
- ZFS will fail to compile against the new kernel
- DKMS errors will appear during package updates
- Your ZFS module will be missing after reboot
- Your Raspberry Pi may fail to boot, even without ZFS-mounted root or critical paths, simply due to systemd or boot scripts expecting the kernel module to be present
Example ZFS Compilation Error:
During package updates or installs, you'll see something like:
checking whether bdev_open_by_path() exists... configure: error: *** None of the expected "blkdev_get_by_path()" interfaces were detected. *** This may be because your kernel version is newer than what is *** supported, or you are using a patched custom kernel with *** incompatible modifications. *** *** ZFS Version: zfs-2.2.3-1~bpo12+1~rpt1 *** Compatible Kernels: 3.10 - 6.7This error means ZFS cannot build its kernel module against Linux 6.12.x, making it unusable.
Why This Happens: The Version Trap
The key problem is that ZFS 2.2.3 remains installed even after a kernel upgrade, and it doesn't get upgraded automatically during
apt upgrade. Since ZFS 2.2.3 only supports up to kernel 6.7, it fails to compile against 6.12.x.However, if you remove and then reinstall ZFS, the package manager installs ZFS 2.3.1, which does support Linux kernel 6.12.x. This version transition is what resolves the issue — but only if you explicitly purge and reinstall ZFS.
Worst Case: The System That Wouldn’t Boot
After upgrading the kernel and rebooting, the system failed to boot properly. It showed errors like:
cannot open access to console, the root account is locked
Although the system did not have critical filesystems on ZFS, the boot process still stalled because system services attempted to load the ZFS kernel module, which was no longer available. This resulted in an unrecoverable boot failure.
The only way forward was to reformat and reinstall Raspberry Pi OS. However, the default Raspberry Pi OS image still comes with a 6.6.x kernel, which is incompatible with ZFS 2.3.1 and newer kernels unless upgraded. Therefore, the recovery process requires one crucial step:
- First, perform a full system upgrade:
sudo apt update && sudo apt full-upgradeThis brings the kernel up to 6.12.x.
- Then, reinstall ZFS:
sudo apt install zfs-dkms zfsutils-linuxOnce this is complete, your system will be running kernel 6.12 with ZFS 2.3.1, and you can safely import your pools and resume operations.
Best Case Recovery: Clean Cut, Clean Upgrade
For users who can still log into their system, here's the cleanest and safest sequence to move forward:
- Stop all services using ZFS, including Docker, NFS, Samba, backup tools, etc.
- Export all ZFS pools:
sudo zpool export -a3. Disable swap if it lives on a ZFS vdev:sudo swapoff /dev/sdXn4. Purge ZFS packages:sudo apt purge zfsutils-linux zfs-dkms zfs-zed sudo rm -rf /usr/src/zfs* /var/lib/dkms/zfs5. Update the kernel to the desired version:sudo apt update && sudo apt full-upgrade6. Reboot into the new kernel:sudo reboot7. Reinstall ZFS:sudo apt install zfs-dkms zfsutils-linux8. Import your pool(s):sudo zpool import poolname9. Restart services that depend on ZFS.
Final Notes: Prevention Is Better Than Recovery
To avoid this issue in the future:
- Hold your current working kernel version:
sudo apt-mark hold linux-image-rpi-v8 linux-headers-rpi-v8* Or track ZFS GitHub for kernel compatibility before upgrading * Or test upgrades on a second Pi or cloned SD card before rolling them out to production
Conclusion: A Solvable Trap
ZFS on the Raspberry Pi remains a powerful option, but it demands careful version tracking. If you upgrade responsibly, or recover cleanly as described above, you can continue benefiting from advanced features like snapshots, send/receive, and compression even on this tiny powerhouse.
Don’t let a kernel update ruin your storage plans—with preparation, the Pi + ZFS combo can remain stable and strong.
-
 @ ccb30bfc:90b6869f
2025-05-02 03:23:40
@ ccb30bfc:90b6869f
2025-05-02 03:23:40A busca por diversão online segura e variada levou muitos jogadores a conhecer a plataforma 98A, que tem ganhado destaque no Brasil por seu excelente desempenho técnico, suporte ao cliente de qualidade e, claro, uma vasta biblioteca de jogos envolventes.
Ao acessar o 98A, o jogador se depara com uma interface fluida, ideal para quem quer jogar sem complicações. A plataforma foi projetada para funcionar com eficiência tanto em computadores quanto em dispositivos móveis, permitindo jogatinas rápidas e práticas a qualquer momento.
O catálogo de jogos chama a atenção logo de início. São centenas de opções divididas em categorias que vão desde jogos de giro até clássicos de cartas. Cada jogo conta com uma descrição clara, regras bem definidas e modos para iniciantes e avançados. Isso democratiza o acesso, fazendo com que qualquer pessoa possa se divertir, independentemente do seu nível de experiência.
Um dos pontos altos do 98Aé o sistema de bonificações. Novos usuários são recebidos com recompensas logo no cadastro, enquanto os jogadores frequentes acumulam benefícios conforme sua atividade na plataforma. Esses prêmios vão desde bônus de crédito até acesso antecipado a novos lançamentos e torneios temáticos.
Além disso, o ambiente do 98A é fortemente voltado para a comunidade. Através de chats ao vivo e quadros de líderes, os jogadores podem interagir, trocar dicas e acompanhar o desempenho de outros participantes. Isso transforma o simples ato de jogar em uma atividade social e divertida.
A plataforma é completamente adaptada à realidade brasileira, com opções de pagamento locais e atendimento em português. Isso garante uma experiência personalizada, segura e acessível. A equipe de suporte, sempre presente, reforça o compromisso com a excelência no atendimento.
Combinando diversidade, inovação e suporte de qualidade, o 98A se posiciona como uma escolha certeira para quem busca diversão e praticidade em um só lugar.
-
 @ ccb30bfc:90b6869f
2025-05-02 03:23:04
@ ccb30bfc:90b6869f
2025-05-02 03:23:04O mundo dos jogos online está em constante evolução, e a BRRBet surge como uma das líderes nesse cenário. Com foco no público brasileiro, a plataforma oferece um ambiente completo, seguro e recheado de opções para quem quer relaxar e se divertir de maneira prática.
Logo ao acessar o site, o usuário se depara com um layout moderno, com menus bem organizados e uma estética agradável. Todo o conteúdo está em português, o que facilita a navegação e torna a experiência muito mais amigável para quem está começando agora.
A BRRBet disponibiliza uma seleção de jogos que agrada a todos os gostos. Seja você fã de jogos de cartas, roleta, slots com temas variados ou experiências ao vivo, há sempre algo novo para explorar. Os jogos são fornecidos por estúdios renomados, garantindo qualidade gráfica, fluidez e mecânicas justas.
Outro atrativo da plataforma são as apostas esportivas. A BRRBet cobre diversos campeonatos nacionais e internacionais, permitindo que o usuário aposte em tempo real e acompanhe as estatísticas das partidas diretamente na tela. Isso traz ainda mais emoção para quem acompanha o mundo esportivo.
No aspecto da experiência do usuário, a BRRBet dá show. O processo de registro é rápido, os métodos de pagamento são variados e seguros, e os saques são processados com agilidade. O suporte ao cliente funciona 24 horas por dia, com atendentes preparados para resolver qualquer dúvida.
A plataforma também oferece recompensas aos jogadores, como bônus de boas-vindas, giros grátis e programas de fidelidade que beneficiam os usuários mais ativos. Tudo isso contribui para tornar a experiência contínua, divertida e cheia de surpresas agradáveis.
Outro ponto que merece destaque é o compromisso com o jogo responsável. A BRRBet disponibiliza ferramentas que permitem ao usuário controlar seus gastos e tempo de uso, promovendo uma experiência equilibrada e saudável.
Portanto, se você procura uma plataforma confiável, divertida e feita para o público brasileiro, a BRRBet é uma excelente escolha. Experimente, explore e descubra um novo nível de entretenimento online com uma plataforma que valoriza cada momento do seu tempo.
-
 @ 7c082548:0b32521e
2025-05-02 03:22:36
@ 7c082548:0b32521e
2025-05-02 03:22:36TQ247 là một nền tảng giải trí trực tuyến được thiết kế để mang đến cho người dùng những trải nghiệm mới mẻ và đầy thú vị. Với giao diện người dùng đơn giản, dễ sử dụng và phong cách thiết kế hiện đại, TQ247 mang đến một không gian giải trí tuyệt vời, nơi người tham gia có thể dễ dàng truy cập vào các trò chơi và dịch vụ đa dạng. Từ những trò chơi trí tuệ giúp kích thích tư duy cho đến những trò chơi hành động đầy kịch tính, TQ247 đều đáp ứng được nhu cầu giải trí của người tham gia ở mọi lứa tuổi. Nền tảng này không ngừng cải tiến và cập nhật các tính năng mới, nhằm đem lại những trải nghiệm mượt mà và hấp dẫn hơn nữa cho người tham gia. TQ247 cũng tổ chức thường xuyên các sự kiện và chương trình khuyến mãi, giúp người tham gia có cơ hội nhận được các phần thưởng hấp dẫn và gia tăng hứng thú khi tham gia các hoạt động giải trí.
Bảo mật luôn là yếu tố quan trọng mà TQ247 đặt lên hàng đầu. Nền tảng này sử dụng các công nghệ bảo mật tiên tiến để đảm bảo rằng mọi thông tin cá nhân của người tham gia đều được bảo vệ an toàn tuyệt đối. TQ247 cam kết không chia sẻ thông tin người dùng với bất kỳ bên thứ ba nào và luôn đảm bảo rằng mọi giao dịch tài chính diễn ra trên nền tảng đều được mã hóa và xử lý cẩn thận. Hệ thống bảo mật của TQ247 luôn được nâng cấp liên tục để đối phó với các mối nguy hiểm và các lỗ hổng bảo mật mới, giúp người tham gia có thể hoàn toàn yên tâm khi tham gia vào các hoạt động giải trí. Bên cạnh đó, dịch vụ chăm sóc khách hàng của TQ247 luôn hoạt động 24/7, với đội ngũ nhân viên tận tình, sẵn sàng hỗ trợ và giải đáp mọi thắc mắc của người tham gia, đảm bảo rằng mọi vấn đề đều được xử lý một cách nhanh chóng và hiệu quả.
Không chỉ chú trọng đến các yếu tố về bảo mật và chất lượng dịch vụ, TQ247 còn đặc biệt quan tâm đến việc xây dựng một cộng đồng người tham gia thân thiện và gắn kết. Nền tảng này thường xuyên tổ chức các hoạt động giao lưu, các sự kiện đặc biệt và chương trình khuyến mãi hấp dẫn để người tham gia có cơ hội gặp gỡ, kết nối và chia sẻ những trải nghiệm giải trí tuyệt vời. TQ247 hiểu rằng việc tạo ra một cộng đồng mạnh mẽ và tích cực không chỉ giúp người tham gia có những phút giây vui vẻ mà còn tạo cơ hội học hỏi và phát triển. Nền tảng này luôn lắng nghe và tiếp nhận ý kiến phản hồi từ cộng đồng người tham gia để cải thiện và nâng cao chất lượng dịch vụ, từ đó đáp ứng tốt hơn nhu cầu của người dùng. Chính sự kết hợp hoàn hảo giữa các trò chơi thú vị, bảo mật an toàn và cộng đồng người tham gia năng động đã giúp TQ247 trở thành một trong những nền tảng giải trí trực tuyến đáng tin cậy và được yêu thích hiện nay.
-
 @ 7c082548:0b32521e
2025-05-02 03:20:12
@ 7c082548:0b32521e
2025-05-02 03:20:12KO66 là nền tảng giải trí trực tuyến nổi bật, được nhiều người tham gia yêu thích nhờ sự đa dạng trong các trò chơi và hoạt động giải trí. Với giao diện trực quan, dễ sử dụng và các tính năng tiện ích, KO66 mang đến cho người tham gia những trải nghiệm thú vị và mượt mà. Người dùng có thể dễ dàng truy cập vào các trò chơi hấp dẫn, từ các trò chơi trí tuệ đến những thử thách hành động đầy kịch tính. Hệ thống trò chơi trên KO66 luôn được cập nhật liên tục, đảm bảo rằng người tham gia luôn có những trải nghiệm mới mẻ và không bị nhàm chán. Ngoài các trò chơi giải trí, KO66 còn cung cấp các dịch vụ khác như các sự kiện và chương trình khuyến mãi hấp dẫn, tạo ra cơ hội để người tham gia có thể trải nghiệm nhiều hoạt động giải trí thú vị và đầy hứng khởi.
Bảo mật là một yếu tố quan trọng mà KO66 luôn chú trọng, nhằm đảm bảo sự an toàn cho thông tin cá nhân và các giao dịch tài chính của người tham gia. Nền tảng này sử dụng các công nghệ bảo mật tiên tiến để mã hóa dữ liệu, giúp bảo vệ người tham gia khỏi các mối đe dọa và rủi ro từ các bên thứ ba. Các thông tin cá nhân và giao dịch tài chính luôn được xử lý một cách cẩn thận và bảo mật tuyệt đối. Người tham gia có thể hoàn toàn yên tâm khi tham gia các hoạt động trên KO66, vì nền tảng này luôn đặt sự an toàn và bảo mật của người dùng lên hàng đầu. Ngoài ra, KO66 còn cung cấp dịch vụ chăm sóc khách hàng chuyên nghiệp và tận tình, với đội ngũ nhân viên luôn sẵn sàng hỗ trợ giải đáp mọi thắc mắc và giúp đỡ người tham gia trong mọi tình huống. Dịch vụ hỗ trợ khách hàng của KO66 hoạt động 24/7, đảm bảo người dùng luôn nhận được sự hỗ trợ nhanh chóng và kịp thời.
Ngoài việc chú trọng đến chất lượng dịch vụ và bảo mật, KO66 còn đặc biệt quan tâm đến việc xây dựng cộng đồng người tham gia gắn kết và tích cực. Nền tảng này tổ chức các sự kiện giao lưu và các chương trình khuyến mãi hấp dẫn, giúp người tham gia có cơ hội kết nối, chia sẻ kinh nghiệm và khám phá thêm nhiều hoạt động giải trí mới mẻ. Các sự kiện này không chỉ mang lại những phần thưởng giá trị mà còn tạo ra không gian giao lưu, học hỏi, giúp cộng đồng người tham gia ngày càng trở nên năng động và sáng tạo. KO66 luôn lắng nghe và tiếp thu ý kiến phản hồi từ người tham gia để cải thiện và nâng cao chất lượng dịch vụ, từ đó đáp ứng tốt hơn nhu cầu giải trí của người dùng. Chính sự kết hợp giữa các trò chơi hấp dẫn, bảo mật an toàn và các hoạt động cộng đồng sôi động đã giúp KO66 trở thành một nền tảng giải trí trực tuyến đáng tin cậy và ngày càng được ưa chuộng.
-
 @ 4ba8e86d:89d32de4
2025-04-28 22:39:20
@ 4ba8e86d:89d32de4
2025-04-28 22:39:20Como funciona o PGP.
O texto a seguir foi retirado do capítulo 1 do documento Introdução à criptografia na documentação do PGP 6.5.1. Copyright © 1990-1999 Network Associates, Inc. Todos os direitos reservados.
-O que é criptografia? -Criptografia forte -Como funciona a criptografia? -Criptografia convencional -Cifra de César -Gerenciamento de chaves e criptografia convencional -Criptografia de chave pública -Como funciona o PGP - Chaves • Assinaturas digitais -Funções hash • Certificados digitais -Distribuição de certificados -Formatos de certificado •Validade e confiança -Verificando validade -Estabelecendo confiança -Modelos de confiança • Revogação de certificado -Comunicar que um certificado foi revogado -O que é uma senha? -Divisão de chave
Os princípios básicos da criptografia.
Quando Júlio César enviou mensagens aos seus generais, ele não confiou nos seus mensageiros. Então ele substituiu cada A em suas mensagens por um D, cada B por um E, e assim por diante através do alfabeto. Somente alguém que conhecesse a regra “shift by 3” poderia decifrar suas mensagens. E assim começamos.
Criptografia e descriptografia.
Os dados que podem ser lidos e compreendidos sem quaisquer medidas especiais são chamados de texto simples ou texto não criptografado. O método de disfarçar o texto simples de forma a ocultar sua substância é chamado de criptografia. Criptografar texto simples resulta em um jargão ilegível chamado texto cifrado. Você usa criptografia para garantir que as informações sejam ocultadas de qualquer pessoa a quem não se destinam, mesmo daqueles que podem ver os dados criptografados. O processo de reverter o texto cifrado ao texto simples original é chamado de descriptografia . A Figura 1-1 ilustra esse processo.
https://image.nostr.build/0e2fcb71ed86a6083e083abbb683f8c103f44a6c6db1aeb2df10ae51ec97ebe5.jpg
Figura 1-1. Criptografia e descriptografia
O que é criptografia?
Criptografia é a ciência que usa a matemática para criptografar e descriptografar dados. A criptografia permite armazenar informações confidenciais ou transmiti-las através de redes inseguras (como a Internet) para que não possam ser lidas por ninguém, exceto pelo destinatário pretendido. Embora a criptografia seja a ciência que protege os dados, a criptoanálise é a ciência que analisa e quebra a comunicação segura. A criptoanálise clássica envolve uma combinação interessante de raciocínio analítico, aplicação de ferramentas matemáticas, descoberta de padrões, paciência, determinação e sorte. Os criptoanalistas também são chamados de atacantes. A criptologia abrange tanto a criptografia quanto a criptoanálise.
Criptografia forte.
"Existem dois tipos de criptografia neste mundo: a criptografia que impedirá a sua irmã mais nova de ler os seus arquivos, e a criptografia que impedirá os principais governos de lerem os seus arquivos. Este livro é sobre o último." --Bruce Schneier, Criptografia Aplicada: Protocolos, Algoritmos e Código Fonte em C. PGP também trata deste último tipo de criptografia. A criptografia pode ser forte ou fraca, conforme explicado acima. A força criptográfica é medida no tempo e nos recursos necessários para recuperar o texto simples. O resultado de uma criptografia forte é um texto cifrado que é muito difícil de decifrar sem a posse da ferramenta de decodificação apropriada. Quão díficil? Dado todo o poder computacional e o tempo disponível de hoje – mesmo um bilhão de computadores fazendo um bilhão de verificações por segundo – não é possível decifrar o resultado de uma criptografia forte antes do fim do universo. Alguém poderia pensar, então, que uma criptografia forte resistiria muito bem até mesmo contra um criptoanalista extremamente determinado. Quem pode realmente dizer? Ninguém provou que a criptografia mais forte disponível hoje resistirá ao poder computacional de amanhã. No entanto, a criptografia forte empregada pelo PGP é a melhor disponível atualmente.
Contudo, a vigilância e o conservadorismo irão protegê-lo melhor do que as alegações de impenetrabilidade.
Como funciona a criptografia?
Um algoritmo criptográfico, ou cifra, é uma função matemática usada no processo de criptografia e descriptografia. Um algoritmo criptográfico funciona em combinação com uma chave – uma palavra, número ou frase – para criptografar o texto simples. O mesmo texto simples é criptografado em texto cifrado diferente com chaves diferentes. A segurança dos dados criptografados depende inteiramente de duas coisas: a força do algoritmo criptográfico e o sigilo da chave. Um algoritmo criptográfico, mais todas as chaves possíveis e todos os protocolos que o fazem funcionar constituem um criptossistema. PGP é um criptossistema.
Criptografia convencional.
Na criptografia convencional, também chamada de criptografia de chave secreta ou de chave simétrica , uma chave é usada tanto para criptografia quanto para descriptografia. O Data Encryption Standard (DES) é um exemplo de criptossistema convencional amplamente empregado pelo Governo Federal. A Figura 1-2 é uma ilustração do processo de criptografia convencional. https://image.nostr.build/328b73ebaff84c949df2560bbbcec4bc3b5e3a5163d5fbb2ec7c7c60488f894c.jpg
Figura 1-2. Criptografia convencional
Cifra de César.
Um exemplo extremamente simples de criptografia convencional é uma cifra de substituição. Uma cifra de substituição substitui uma informação por outra. Isso é feito com mais frequência compensando as letras do alfabeto. Dois exemplos são o Anel Decodificador Secreto do Capitão Meia-Noite, que você pode ter possuído quando era criança, e a cifra de Júlio César. Em ambos os casos, o algoritmo serve para compensar o alfabeto e a chave é o número de caracteres para compensá-lo. Por exemplo, se codificarmos a palavra "SEGREDO" usando o valor chave de César de 3, deslocaremos o alfabeto para que a terceira letra abaixo (D) comece o alfabeto. Então começando com A B C D E F G H I J K L M N O P Q R S T U V W X Y Z e deslizando tudo para cima em 3, você obtém DEFGHIJKLMNOPQRSTUVWXYZABC onde D=A, E=B, F=C e assim por diante. Usando este esquema, o texto simples, "SECRET" é criptografado como "VHFUHW". Para permitir que outra pessoa leia o texto cifrado, você diz a ela que a chave é 3. Obviamente, esta é uma criptografia extremamente fraca para os padrões atuais, mas, ei, funcionou para César e ilustra como funciona a criptografia convencional.
Gerenciamento de chaves e criptografia convencional.
A criptografia convencional tem benefícios. É muito rápido. É especialmente útil para criptografar dados que não vão a lugar nenhum. No entanto, a criptografia convencional por si só como meio de transmissão segura de dados pode ser bastante cara, simplesmente devido à dificuldade de distribuição segura de chaves. Lembre-se de um personagem do seu filme de espionagem favorito: a pessoa com uma pasta trancada e algemada ao pulso. Afinal, o que há na pasta? Provavelmente não é o código de lançamento de mísseis/fórmula de biotoxina/plano de invasão em si. É a chave que irá descriptografar os dados secretos. Para que um remetente e um destinatário se comuniquem com segurança usando criptografia convencional, eles devem chegar a um acordo sobre uma chave e mantê-la secreta entre si. Se estiverem em locais físicos diferentes, devem confiar em um mensageiro, no Bat Phone ou em algum outro meio de comunicação seguro para evitar a divulgação da chave secreta durante a transmissão. Qualquer pessoa que ouvir ou interceptar a chave em trânsito poderá posteriormente ler, modificar e falsificar todas as informações criptografadas ou autenticadas com essa chave. Do DES ao Anel Decodificador Secreto do Capitão Midnight, o problema persistente com a criptografia convencional é a distribuição de chaves: como você leva a chave ao destinatário sem que alguém a intercepte?
Criptografia de chave pública.
Os problemas de distribuição de chaves são resolvidos pela criptografia de chave pública, cujo conceito foi introduzido por Whitfield Diffie e Martin Hellman em 1975. (Há agora evidências de que o Serviço Secreto Britânico a inventou alguns anos antes de Diffie e Hellman, mas a manteve um segredo militar - e não fez nada com isso.
[JH Ellis: The Possibility of Secure Non-Secret Digital Encryption, CESG Report, January 1970]) A criptografia de chave pública é um esquema assimétrico que usa um par de chaves para criptografia: uma chave pública, que criptografa os dados, e uma chave privada ou secreta correspondente para descriptografia. Você publica sua chave pública para o mundo enquanto mantém sua chave privada em segredo. Qualquer pessoa com uma cópia da sua chave pública pode criptografar informações que somente você pode ler. Até mesmo pessoas que você nunca conheceu. É computacionalmente inviável deduzir a chave privada da chave pública. Qualquer pessoa que possua uma chave pública pode criptografar informações, mas não pode descriptografá-las. Somente a pessoa que possui a chave privada correspondente pode descriptografar as informações. https://image.nostr.build/fdb71ae7a4450a523456827bdd509b31f0250f63152cc6f4ba78df290887318b.jpg
Figura 1-3. Criptografia de chave pública O principal benefício da criptografia de chave pública é que ela permite que pessoas que não possuem nenhum acordo de segurança pré-existente troquem mensagens com segurança. A necessidade de remetente e destinatário compartilharem chaves secretas através de algum canal seguro é eliminada; todas as comunicações envolvem apenas chaves públicas e nenhuma chave privada é transmitida ou compartilhada. Alguns exemplos de criptossistemas de chave pública são Elgamal (nomeado em homenagem a seu inventor, Taher Elgamal), RSA (nomeado em homenagem a seus inventores, Ron Rivest, Adi Shamir e Leonard Adleman), Diffie-Hellman (nomeado, você adivinhou, em homenagem a seus inventores). ) e DSA, o algoritmo de assinatura digital (inventado por David Kravitz). Como a criptografia convencional já foi o único meio disponível para transmitir informações secretas, o custo dos canais seguros e da distribuição de chaves relegou a sua utilização apenas àqueles que podiam pagar, como governos e grandes bancos (ou crianças pequenas com anéis descodificadores secretos). A criptografia de chave pública é a revolução tecnológica que fornece criptografia forte para as massas adultas. Lembra do mensageiro com a pasta trancada e algemada ao pulso? A criptografia de chave pública o tira do mercado (provavelmente para seu alívio).
Como funciona o PGP.
O PGP combina alguns dos melhores recursos da criptografia convencional e de chave pública. PGP é um criptossistema híbrido. Quando um usuário criptografa texto simples com PGP, o PGP primeiro compacta o texto simples. A compactação de dados economiza tempo de transmissão do modem e espaço em disco e, mais importante ainda, fortalece a segurança criptográfica. A maioria das técnicas de criptoanálise explora padrões encontrados no texto simples para quebrar a cifra. A compressão reduz esses padrões no texto simples, aumentando assim enormemente a resistência à criptoanálise. (Arquivos que são muito curtos para compactar ou que não são compactados bem não são compactados.) O PGP então cria uma chave de sessão, que é uma chave secreta única. Esta chave é um número aleatório gerado a partir dos movimentos aleatórios do mouse e das teclas digitadas. Esta chave de sessão funciona com um algoritmo de criptografia convencional rápido e muito seguro para criptografar o texto simples; o resultado é texto cifrado. Depois que os dados são criptografados, a chave da sessão é criptografada na chave pública do destinatário. Essa chave de sessão criptografada com chave pública é transmitida junto com o texto cifrado ao destinatário.
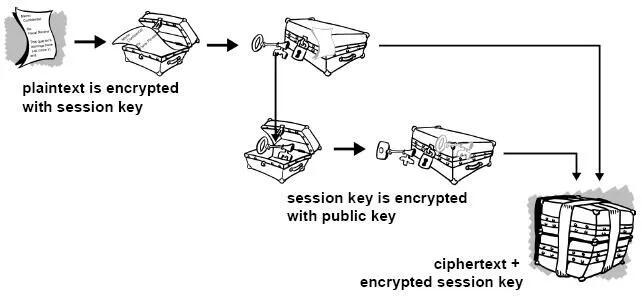
Figura 1-4. Como funciona a criptografia PGP A descriptografia funciona ao contrário. A cópia do PGP do destinatário usa sua chave privada para recuperar a chave de sessão temporária, que o PGP usa para descriptografar o texto cifrado criptografado convencionalmente.

Figura 1-5. Como funciona a descriptografia PGP A combinação dos dois métodos de criptografia combina a conveniência da criptografia de chave pública com a velocidade da criptografia convencional. A criptografia convencional é cerca de 1.000 vezes mais rápida que a criptografia de chave pública. A criptografia de chave pública, por sua vez, fornece uma solução para
problemas de distribuição de chaves e transmissão de dados. Usados em conjunto, o desempenho e a distribuição de chaves são melhorados sem qualquer sacrifício na segurança.
Chaves.
Uma chave é um valor que funciona com um algoritmo criptográfico para produzir um texto cifrado específico. As chaves são basicamente números muito, muito, muito grandes. O tamanho da chave é medido em bits; o número que representa uma chave de 1024 bits é enorme. Na criptografia de chave pública, quanto maior a chave, mais seguro é o texto cifrado. No entanto, o tamanho da chave pública e o tamanho da chave secreta da criptografia convencional não têm nenhuma relação. Uma chave convencional de 80 bits tem a força equivalente a uma chave pública de 1.024 bits. Uma chave convencional de 128 bits é equivalente a uma chave pública de 3.000 bits. Novamente, quanto maior a chave, mais segura, mas os algoritmos usados para cada tipo de criptografia são muito diferentes e, portanto, a comparação é como a de maçãs com laranjas. Embora as chaves pública e privada estejam matematicamente relacionadas, é muito difícil derivar a chave privada dada apenas a chave pública; no entanto, derivar a chave privada é sempre possível, desde que haja tempo e capacidade computacional suficientes. Isto torna muito importante escolher chaves do tamanho certo; grande o suficiente para ser seguro, mas pequeno o suficiente para ser aplicado rapidamente. Além disso, você precisa considerar quem pode estar tentando ler seus arquivos, quão determinados eles estão, quanto tempo têm e quais podem ser seus recursos. Chaves maiores serão criptograficamente seguras por um longo período de tempo. Se o que você deseja criptografar precisar ficar oculto por muitos anos, você pode usar uma chave muito grande. Claro, quem sabe quanto tempo levará para determinar sua chave usando os computadores mais rápidos e eficientes de amanhã? Houve um tempo em que uma chave simétrica de 56 bits era considerada extremamente segura. As chaves são armazenadas de forma criptografada. O PGP armazena as chaves em dois arquivos no seu disco rígido; um para chaves públicas e outro para chaves privadas. Esses arquivos são chamados de chaveiros. Ao usar o PGP, você normalmente adicionará as chaves públicas dos seus destinatários ao seu chaveiro público. Suas chaves privadas são armazenadas em seu chaveiro privado. Se você perder seu chaveiro privado, não será possível descriptografar nenhuma informação criptografada nas chaves desse anel.
Assinaturas digitais.
Um grande benefício da criptografia de chave pública é que ela fornece um método para empregar assinaturas digitais. As assinaturas digitais permitem ao destinatário da informação verificar a autenticidade da origem da informação e também verificar se a informação está intacta. Assim, as assinaturas digitais de chave pública fornecem autenticação e integridade de dados. A assinatura digital também proporciona o não repúdio, o que significa que evita que o remetente alegue que não enviou realmente as informações. Esses recursos são tão fundamentais para a criptografia quanto a privacidade, se não mais. Uma assinatura digital tem a mesma finalidade de uma assinatura manuscrita. No entanto, uma assinatura manuscrita é fácil de falsificar. Uma assinatura digital é superior a uma assinatura manuscrita porque é quase impossível de ser falsificada, além de atestar o conteúdo da informação, bem como a identidade do signatário.
Algumas pessoas tendem a usar mais assinaturas do que criptografia. Por exemplo, você pode não se importar se alguém souber que você acabou de depositar US$ 1.000 em sua conta, mas quer ter certeza de que foi o caixa do banco com quem você estava lidando. A maneira básica pela qual as assinaturas digitais são criadas é ilustrada na Figura 1-6 . Em vez de criptografar informações usando a chave pública de outra pessoa, você as criptografa com sua chave privada. Se as informações puderem ser descriptografadas com sua chave pública, elas deverão ter se originado em você.
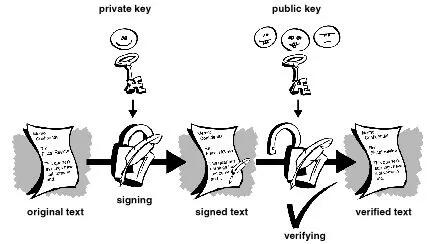
Figura 1-6. Assinaturas digitais simples
Funções hash.
O sistema descrito acima apresenta alguns problemas. É lento e produz um enorme volume de dados – pelo menos o dobro do tamanho da informação original. Uma melhoria no esquema acima é a adição de uma função hash unidirecional no processo. Uma função hash unidirecional recebe uma entrada de comprimento variável – neste caso, uma mensagem de qualquer comprimento, até mesmo milhares ou milhões de bits – e produz uma saída de comprimento fixo; digamos, 160 bits. A função hash garante que, se a informação for alterada de alguma forma – mesmo que por apenas um bit – seja produzido um valor de saída totalmente diferente. O PGP usa uma função hash criptograficamente forte no texto simples que o usuário está assinando. Isso gera um item de dados de comprimento fixo conhecido como resumo da mensagem. (Novamente, qualquer alteração nas informações resulta em um resumo totalmente diferente.) Então o PGP usa o resumo e a chave privada para criar a “assinatura”. O PGP transmite a assinatura e o texto simples juntos. Ao receber a mensagem, o destinatário utiliza o PGP para recalcular o resumo, verificando assim a assinatura. O PGP pode criptografar o texto simples ou não; assinar texto simples é útil se alguns dos destinatários não estiverem interessados ou não forem capazes de verificar a assinatura. Desde que uma função hash segura seja usada, não há como retirar a assinatura de alguém de um documento e anexá-la a outro, ou alterar uma mensagem assinada de qualquer forma. A menor alteração em um documento assinado causará falha no processo de verificação da assinatura digital.
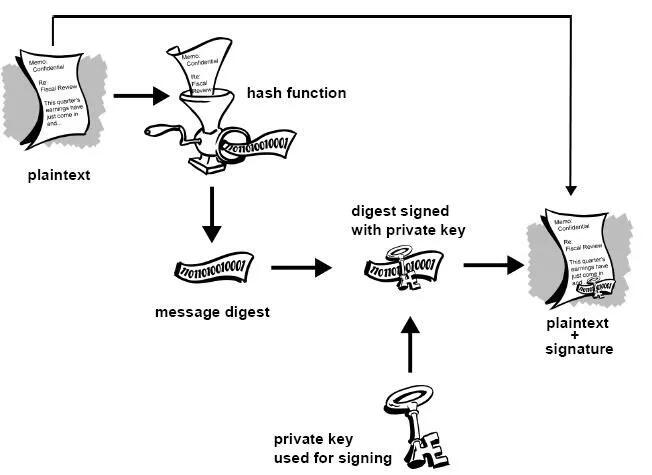
Figura 1-7. Assinaturas digitais seguras As assinaturas digitais desempenham um papel importante na autenticação e validação de chaves de outros usuários PGP.
Certificados digitais.
Um problema com os criptosistemas de chave pública é que os usuários devem estar constantemente vigilantes para garantir que estão criptografando com a chave da pessoa correta. Num ambiente onde é seguro trocar chaves livremente através de servidores públicos, os ataques man-in-the-middle são uma ameaça potencial. Neste tipo de ataque, alguém publica uma chave falsa com o nome e ID de usuário do destinatário pretendido. Os dados criptografados – e interceptados por – o verdadeiro proprietário desta chave falsa estão agora em mãos erradas. Em um ambiente de chave pública, é vital que você tenha certeza de que a chave pública para a qual você está criptografando os dados é de fato a chave pública do destinatário pretendido e não uma falsificação. Você pode simplesmente criptografar apenas as chaves que foram entregues fisicamente a você. Mas suponha que você precise trocar informações com pessoas que nunca conheceu; como você pode saber se tem a chave correta? Os certificados digitais, ou certs, simplificam a tarefa de estabelecer se uma chave pública realmente pertence ao suposto proprietário. Um certificado é uma forma de credencial. Exemplos podem ser sua carteira de motorista, seu cartão de previdência social ou sua certidão de nascimento. Cada um deles contém algumas informações que identificam você e alguma autorização informando que outra pessoa confirmou sua identidade. Alguns certificados, como o seu passaporte, são uma confirmação importante o suficiente da sua identidade para que você não queira perdê-los, para que ninguém os use para se passar por você.
Um certificado digital são dados que funcionam como um certificado físico. Um certificado digital é uma informação incluída na chave pública de uma pessoa que ajuda outras pessoas a verificar se uma chave é genuína ou válida. Os certificados digitais são usados para impedir tentativas de substituir a chave de uma pessoa por outra.
Um certificado digital consiste em três coisas:
● Uma chave pública.
● Informações do certificado. (Informações de "identidade" sobre o usuário, como nome, ID do usuário e assim por diante.) ● Uma ou mais assinaturas digitais.
O objetivo da assinatura digital em um certificado é afirmar que as informações do certificado foram atestadas por alguma outra pessoa ou entidade. A assinatura digital não atesta a autenticidade do certificado como um todo; ele atesta apenas que as informações de identidade assinadas acompanham ou estão vinculadas à chave pública. Assim, um certificado é basicamente uma chave pública com uma ou duas formas de identificação anexadas, além de um forte selo de aprovação de algum outro indivíduo confiável.
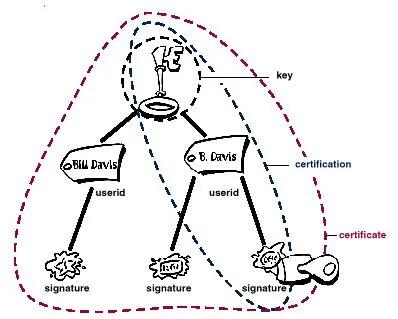 Figura 1-8. Anatomia de um certificado PGP
Figura 1-8. Anatomia de um certificado PGPDistribuição de certificados.
Os certificados são utilizados quando é necessário trocar chaves públicas com outra pessoa. Para pequenos grupos de pessoas que desejam se comunicar com segurança, é fácil trocar manualmente disquetes ou e-mails contendo a chave pública de cada proprietário. Esta é a distribuição manual de chave pública e é prática apenas até certo ponto. Além desse ponto, é necessário implementar sistemas que possam fornecer os mecanismos necessários de segurança, armazenamento e troca para que colegas de trabalho, parceiros de negócios ou estranhos possam se comunicar, se necessário. Eles podem vir na forma de repositórios somente de armazenamento, chamados Servidores de Certificados, ou sistemas mais estruturados que fornecem recursos adicionais de gerenciamento de chaves e são chamados de Infraestruturas de Chave Pública (PKIs).
Servidores de certificados.
Um servidor de certificados, também chamado de servidor certificado ou servidor de chaves, é um banco de dados que permite aos usuários enviar e recuperar certificados digitais. Um servidor certificado geralmente fornece alguns recursos administrativos que permitem que uma empresa mantenha suas políticas de segurança – por exemplo, permitindo que apenas as chaves que atendam a determinados requisitos sejam armazenadas.
Infraestruturas de Chave Pública.
Uma PKI contém os recursos de armazenamento de certificados de um servidor de certificados, mas também fornece recursos de gerenciamento de certificados (a capacidade de emitir, revogar, armazenar, recuperar e confiar em certificados). A principal característica de uma PKI é a introdução do que é conhecido como Autoridade Certificadora,ou CA, que é uma entidade humana — uma pessoa, grupo, departamento, empresa ou outra associação — que uma organização autorizou a emitir certificados para seus usuários de computador. (A função de uma CA é análoga à do Passport Office do governo de um país.) Uma CA cria certificados e os assina digitalmente usando a chave privada da CA. Devido ao seu papel na criação de certificados, a CA é o componente central de uma PKI. Usando a chave pública da CA, qualquer pessoa que queira verificar a autenticidade de um certificado verifica a assinatura digital da CA emissora e, portanto, a integridade do conteúdo do certificado (mais importante ainda, a chave pública e a identidade do titular do certificado).
Formatos de certificado.
Um certificado digital é basicamente uma coleção de informações de identificação vinculadas a uma chave pública e assinadas por um terceiro confiável para provar sua autenticidade. Um certificado digital pode ter vários formatos diferentes.
O PGP reconhece dois formatos de certificado diferentes:
● Certificados PGP ● Certificados X.509 Formato do certificado PGP. Um certificado PGP inclui (mas não está limitado a) as seguintes informações: ● O número da versão do PGP — identifica qual versão do PGP foi usada para criar a chave associada ao certificado. A chave pública do titular do certificado — a parte pública do seu par de chaves, juntamente com o algoritmo da chave: RSA, DH (Diffie-Hellman) ou DSA (Algoritmo de Assinatura Digital).
● As informações do detentor do certificado — consistem em informações de “identidade” sobre o usuário, como seu nome, ID de usuário, fotografia e assim por diante. ● A assinatura digital do proprietário do certificado — também chamada de autoassinatura, é a assinatura que utiliza a chave privada correspondente da chave pública associada ao certificado. ● O período de validade do certificado — a data/hora de início e a data/hora de expiração do certificado; indica quando o certificado irá expirar. ● O algoritmo de criptografia simétrica preferido para a chave — indica o algoritmo de criptografia para o qual o proprietário do certificado prefere que as informações sejam criptografadas. Os algoritmos suportados são CAST, IDEA ou Triple-DES. Você pode pensar em um certificado PGP como uma chave pública com um ou mais rótulos vinculados a ele (veja a Figura 1.9 ). Nessas 'etiquetas' você encontrará informações que identificam o proprietário da chave e uma assinatura do proprietário da chave, que afirma que a chave e a identificação andam juntas. (Essa assinatura específica é chamada de autoassinatura; todo certificado PGP contém uma autoassinatura.) Um aspecto único do formato de certificado PGP é que um único certificado pode conter múltiplas assinaturas. Várias ou muitas pessoas podem assinar o par chave/identificação para atestar a sua própria garantia de que a chave pública pertence definitivamente ao proprietário especificado. Se você procurar em um servidor de certificados público, poderá notar que certos certificados, como o do criador do PGP, Phil Zimmermann, contêm muitas assinaturas. Alguns certificados PGP consistem em uma chave pública com vários rótulos, cada um contendo um meio diferente de identificar o proprietário da chave (por exemplo, o nome do proprietário e a conta de e-mail corporativa, o apelido do proprietário e a conta de e-mail residencial, uma fotografia do proprietário — tudo em um certificado). A lista de assinaturas de cada uma dessas identidades pode ser diferente; as assinaturas atestam a autenticidade de que um dos rótulos pertence à chave pública, e não que todos os rótulos da chave sejam autênticos. (Observe que 'autêntico' está nos olhos de quem vê - assinaturas são opiniões, e diferentes pessoas dedicam diferentes níveis de devida diligência na verificação da autenticidade antes de assinar uma chave.)
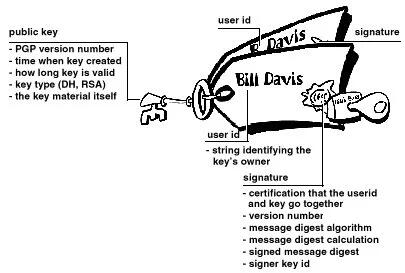 Figura 1-9. Um certificado PGP
Figura 1-9. Um certificado PGPFormato de certificado X.509.
X.509 é outro formato de certificado muito comum. Todos os certificados X.509 estão em conformidade com o padrão internacional ITU-T X.509; assim (teoricamente) os certificados X.509 criados para um aplicativo podem ser usados por qualquer aplicativo compatível com X.509. Na prática, porém, diferentes empresas criaram suas próprias extensões para certificados X.509, e nem todas funcionam juntas. Um certificado exige que alguém valide que uma chave pública e o nome do proprietário da chave andam juntos. Com os certificados PGP, qualquer pessoa pode desempenhar o papel de validador. Com certificados X.509, o validador é sempre uma Autoridade Certificadora ou alguém designado por uma CA. (Tenha em mente que os certificados PGP também suportam totalmente uma estrutura hierárquica usando uma CA para validar certificados.)
Um certificado X.509 é uma coleção de um conjunto padrão de campos contendo informações sobre um usuário ou dispositivo e sua chave pública correspondente. O padrão X.509 define quais informações vão para o certificado e descreve como codificá-lo (o formato dos dados). Todos os certificados X.509 possuem os seguintes dados:
O número da versão X.509
— identifica qual versão do padrão X.509 se aplica a este certificado, o que afeta quais informações podem ser especificadas nele. A mais atual é a versão 3.
A chave pública do titular do certificado
— a chave pública do titular do certificado, juntamente com um identificador de algoritmo que especifica a qual sistema criptográfico a chave pertence e quaisquer parâmetros de chave associados.
O número de série do certificado
— a entidade (aplicação ou pessoa) que criou o certificado é responsável por atribuir-lhe um número de série único para distingui-lo de outros certificados que emite. Esta informação é usada de diversas maneiras; por exemplo, quando um certificado é revogado, seu número de série é colocado em uma Lista de Revogação de Certificados ou CRL.
O identificador exclusivo do detentor do certificado
— (ou DN — nome distinto). Este nome pretende ser exclusivo na Internet. Este nome pretende ser exclusivo na Internet. Um DN consiste em múltiplas subseções e pode ser parecido com isto: CN=Bob Allen, OU=Divisão Total de Segurança de Rede, O=Network Associates, Inc., C=EUA (Referem-se ao nome comum, à unidade organizacional, à organização e ao país do sujeito .)
O período de validade do certificado
— a data/hora de início e a data/hora de expiração do certificado; indica quando o certificado irá expirar.
O nome exclusivo do emissor do certificado
— o nome exclusivo da entidade que assinou o certificado. Normalmente é uma CA. A utilização do certificado implica confiar na entidade que assinou este certificado. (Observe que em alguns casos, como certificados de CA raiz ou de nível superior , o emissor assina seu próprio certificado.)
A assinatura digital do emitente
— a assinatura utilizando a chave privada da entidade que emitiu o certificado.
O identificador do algoritmo de assinatura
— identifica o algoritmo usado pela CA para assinar o certificado.
Existem muitas diferenças entre um certificado X.509 e um certificado PGP, mas as mais importantes são as seguintes: você pode criar seu próprio certificado PGP;
● você deve solicitar e receber um certificado X.509 de uma autoridade de certificação
● Os certificados X.509 suportam nativamente apenas um único nome para o proprietário da chave
● Os certificados X.509 suportam apenas uma única assinatura digital para atestar a validade da chave
Para obter um certificado X.509, você deve solicitar a uma CA a emissão de um certificado. Você fornece sua chave pública, prova de que possui a chave privada correspondente e algumas informações específicas sobre você. Em seguida, você assina digitalmente as informações e envia o pacote completo – a solicitação de certificado – para a CA. A CA então realiza algumas diligências para verificar se as informações fornecidas estão corretas e, em caso afirmativo, gera o certificado e o devolve.
Você pode pensar em um certificado X.509 como um certificado de papel padrão (semelhante ao que você recebeu ao concluir uma aula de primeiros socorros básicos) com uma chave pública colada nele. Ele contém seu nome e algumas informações sobre você, além da assinatura da pessoa que o emitiu para você.
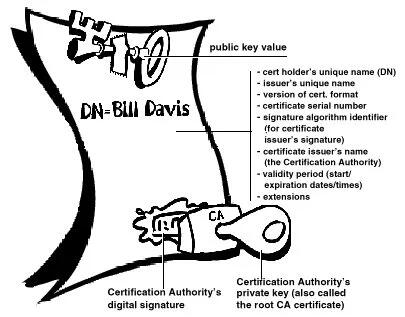
Figura 1-10. Um certificado X.509 Provavelmente, o uso mais visível dos certificados X.509 atualmente é em navegadores da web.
Validade e confiança Cada usuário em um sistema de chave pública está vulnerável a confundir uma chave falsa (certificado) com uma chave real. Validade é a confiança de que um certificado de chave pública pertence ao seu suposto proprietário. A validade é essencial em um ambiente de chave pública onde você deve estabelecer constantemente se um determinado certificado é autêntico ou não. Depois de ter certeza de que um certificado pertencente a outra pessoa é válido, você pode assinar a cópia em seu chaveiro para atestar que verificou o certificado e que ele é autêntico. Se quiser que outras pessoas saibam que você deu ao certificado seu selo de aprovação, você pode exportar a assinatura para um servidor de certificados para que outras pessoas possam vê-la.
Conforme descrito na seção Infraestruturas de Chave Pública , algumas empresas designam uma ou mais Autoridades de Certificação (CAs) para indicar a validade do certificado. Em uma organização que usa uma PKI com certificados X.509, é função da CA emitir certificados aos usuários — um processo que geralmente envolve responder à solicitação de certificado do usuário. Em uma organização que usa certificados PGP sem PKI, é função da CA verificar a autenticidade de todos os certificados PGP e depois assinar os bons. Basicamente, o objetivo principal de uma CA é vincular uma chave pública às informações de identificação contidas no certificado e, assim, garantir a terceiros que algum cuidado foi tomado para garantir que esta ligação das informações de identificação e da chave seja válida. O CA é o Grand Pooh-bah da validação em uma organização; alguém em quem todos confiam e, em algumas organizações, como aquelas que utilizam uma PKI, nenhum certificado é considerado válido, a menos que tenha sido assinado por uma CA confiável.
Verificando validade.
Uma maneira de estabelecer a validade é passar por algum processo manual. Existem várias maneiras de fazer isso. Você pode exigir que o destinatário pretendido lhe entregue fisicamente uma cópia de sua chave pública. Mas isto é muitas vezes inconveniente e ineficiente. Outra forma é verificar manualmente a impressão digital do certificado. Assim como as impressões digitais de cada ser humano são únicas, a impressão digital de cada certificado PGP é única. A impressão digital é um hash do certificado do usuário e aparece como uma das propriedades do certificado. No PGP, a impressão digital pode aparecer como um número hexadecimal ou uma série das chamadas palavras biométricas, que são foneticamente distintas e são usadas para facilitar um pouco o processo de identificação da impressão digital. Você pode verificar se um certificado é válido ligando para o proprietário da chave (para que você origine a transação) e pedindo ao proprietário que leia a impressão digital de sua chave para você e compare essa impressão digital com aquela que você acredita ser a verdadeira. Isso funciona se você conhece a voz do proprietário, mas como verificar manualmente a identidade de alguém que você não conhece? Algumas pessoas colocam a impressão digital de sua chave em seus cartões de visita exatamente por esse motivo. Outra forma de estabelecer a validade do certificado de alguém é confiar que um terceiro indivíduo passou pelo processo de validação do mesmo. Uma CA, por exemplo, é responsável por garantir que, antes de emitir um certificado, ele ou ela o verifique cuidadosamente para ter certeza de que a parte da chave pública realmente pertence ao suposto proprietário. Qualquer pessoa que confie na CA considerará automaticamente quaisquer certificados assinados pela CA como válidos. Outro aspecto da verificação da validade é garantir que o certificado não foi revogado. Para obter mais informações, consulte a seção Revogação de certificado .
Estabelecendo confiança.
Você valida certificados. Você confia nas pessoas. Mais especificamente, você confia nas pessoas para validar os certificados de outras pessoas. Normalmente, a menos que o proprietário lhe entregue o certificado, você terá que confiar na palavra de outra pessoa de que ele é válido.
Introdutores meta e confiáveis.
Na maioria das situações, as pessoas confiam completamente na CA para estabelecer a validade dos certificados. Isso significa que todos os demais dependem da CA para passar por todo o processo de validação manual. Isso é aceitável até um certo número de usuários ou locais de trabalho e, então, não é possível para a AC manter o mesmo nível de validação de qualidade. Nesse caso, é necessário adicionar outros validadores ao sistema.
Um CA também pode ser um meta- introdutor. Um meta-introdutor confere não apenas validade às chaves, mas também confere a capacidade de confiar nas chaves a outros. Semelhante ao rei que entrega seu selo a seus conselheiros de confiança para que eles possam agir de acordo com sua autoridade, o meta-introdutor permite que outros atuem como introdutores de confiança. Esses introdutores confiáveis podem validar chaves com o mesmo efeito do meta-introdutor. Eles não podem, entretanto, criar novos introdutores confiáveis.
Meta-introdutor e introdutor confiável são termos PGP. Em um ambiente X.509, o meta-introdutor é chamado de Autoridade de Certificação raiz ( CA raiz) e os introdutores confiáveis são Autoridades de Certificação subordinadas . A CA raiz usa a chave privada associada a um tipo de certificado especial denominado certificado CA raiz para assinar certificados. Qualquer certificado assinado pelo certificado CA raiz é visto como válido por qualquer outro certificado assinado pela raiz. Este processo de validação funciona mesmo para certificados assinados por outras CAs no sistema — desde que o certificado da CA raiz tenha assinado o certificado da CA subordinada, qualquer certificado assinado pela CA será considerado válido para outras pessoas dentro da hierarquia. Este processo de verificação de backup por meio do sistema para ver quem assinou cujo certificado é chamado de rastreamento de um caminho de certificação ou cadeia de certificação.
Modelos de confiança.
Em sistemas relativamente fechados, como em uma pequena empresa, é fácil rastrear um caminho de certificação até a CA raiz. No entanto, os usuários muitas vezes precisam se comunicar com pessoas fora do seu ambiente corporativo, incluindo algumas que nunca conheceram, como fornecedores, consumidores, clientes, associados e assim por diante. É difícil estabelecer uma linha de confiança com aqueles em quem sua CA não confia explicitamente. As empresas seguem um ou outro modelo de confiança, que determina como os usuários irão estabelecer a validade do certificado. Existem três modelos diferentes:
Confiança Direta.
Confiança Hierárquica Uma teia de confiança Confiança direta A confiança direta é o modelo de confiança mais simples. Neste modelo, um usuário confia que uma chave é válida porque sabe de onde ela veio. Todos os criptosistemas usam essa forma de confiança de alguma forma. Por exemplo, em navegadores da Web, as chaves raiz da Autoridade de Certificação são diretamente confiáveis porque foram enviadas pelo fabricante. Se houver alguma forma de hierarquia, ela se estenderá a partir desses certificados diretamente confiáveis. No PGP, um usuário que valida as chaves e nunca define outro certificado para ser um introdutor confiável está usando confiança direta.
 Figura 1-11. Confiança direta
Figura 1-11. Confiança diretaConfiança Hierárquica.
Em um sistema hierárquico, há vários certificados "raiz" a partir dos quais a confiança se estende. Esses certificados podem certificar eles próprios certificados ou podem certificar certificados que certificam ainda outros certificados em alguma cadeia. Considere isso como uma grande “árvore” de confiança. A validade do certificado "folha" é verificada rastreando desde seu certificador até outros certificadores, até que um certificado raiz diretamente confiável seja encontrado.
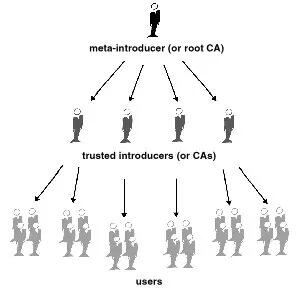
Figura 1-12. Confiança hierárquica
Teia de Confiança.
Uma teia de confiança abrange ambos os outros modelos, mas também acrescenta a noção de que a confiança está nos olhos de quem vê (que é a visão do mundo real) e a ideia de que mais informação é melhor. É, portanto, um modelo de confiança cumulativa. Um certificado pode ser confiável diretamente ou confiável em alguma cadeia que remonta a um certificado raiz diretamente confiável (o meta-introdutor) ou por algum grupo de introdutores.
Talvez você já tenha ouvido falar do termo seis graus de separação, que sugere que qualquer pessoa no mundo pode determinar algum vínculo com qualquer outra pessoa no mundo usando seis ou menos outras pessoas como intermediários. Esta é uma teia de introdutores. É também a visão de confiança do PGP. PGP usa assinaturas digitais como forma de introdução. Quando qualquer usuário assina a chave de outro, ele ou ela se torna o introdutor dessa chave. À medida que esse processo avança, ele estabelece uma rede de confiança.
Em um ambiente PGP, qualquer usuário pode atuar como autoridade certificadora. Qualquer usuário PGP pode validar o certificado de chave pública de outro usuário PGP. No entanto, tal certificado só é válido para outro usuário se a parte confiável reconhecer o validador como um introdutor confiável. (Ou seja, você confia na minha opinião de que as chaves dos outros são válidas apenas se você me considerar um apresentador confiável. Caso contrário, minha opinião sobre a validade das outras chaves é discutível.) Armazenados no chaveiro público de cada usuário estão indicadores de
● se o usuário considera ou não uma chave específica válida
● o nível de confiança que o usuário deposita na chave que o proprietário da chave pode servir como certificador das chaves de terceiros
Você indica, na sua cópia da minha chave, se acha que meu julgamento conta. Na verdade, é um sistema de reputação: certas pessoas têm a reputação de fornecer boas assinaturas e as pessoas confiam nelas para atestar a validade de outras chaves.
Níveis de confiança no PGP.
O nível mais alto de confiança em uma chave, a confiança implícita , é a confiança em seu próprio par de chaves. O PGP assume que se você possui a chave privada, você deve confiar nas ações da sua chave pública relacionada. Quaisquer chaves assinadas pela sua chave implicitamente confiável são válidas.
Existem três níveis de confiança que você pode atribuir à chave pública de outra pessoa:
● Confiança total ● Confiança marginal ● Não confiável (ou não confiável)
Para tornar as coisas confusas, também existem três níveis de validade:
● Válido ● Marginalmente válido ● Inválido
Para definir a chave de outra pessoa como um introdutor confiável, você
- Comece com uma chave válida, que seja.
- assinado por você ou
-
assinado por outro apresentador confiável e então
-
Defina o nível de confiança que você acha que o proprietário da chave tem direito.
Por exemplo, suponha que seu chaveiro contenha a chave de Alice. Você validou a chave de Alice e indica isso assinando-a. Você sabe que Alice é uma verdadeira defensora da validação de chaves de outras pessoas. Portanto, você atribui a chave dela com confiança total. Isso faz de Alice uma Autoridade Certificadora. Se Alice assinar a chave de outra pessoa, ela aparecerá como Válida em seu chaveiro. O PGP requer uma assinatura Totalmente confiável ou duas assinaturas Marginalmente confiáveis para estabelecer uma chave como válida. O método do PGP de considerar dois Marginais iguais a um Completo é semelhante a um comerciante que solicita duas formas de identificação. Você pode considerar Alice bastante confiável e também considerar Bob bastante confiável. Qualquer um deles sozinho corre o risco de assinar acidentalmente uma chave falsificada, portanto, você pode não depositar total confiança em nenhum deles. No entanto, as probabilidades de ambos os indivíduos terem assinado a mesma chave falsa são provavelmente pequenas.
Revogação de certificado.
Os certificados só são úteis enquanto são válidos. Não é seguro simplesmente presumir que um certificado é válido para sempre. Na maioria das organizações e em todas as PKIs, os certificados têm uma vida útil restrita. Isso restringe o período em que um sistema fica vulnerável caso ocorra um comprometimento do certificado.
Os certificados são assim criados com um período de validade programado: uma data/hora de início e uma data/hora de expiração. Espera-se que o certificado seja utilizável durante todo o seu período de validade (seu tempo de vida ). Quando o certificado expirar, ele não será mais válido, pois a autenticidade do seu par chave/identificação não estará mais garantida. (O certificado ainda pode ser usado com segurança para reconfirmar informações que foram criptografadas ou assinadas dentro do período de validade – no entanto, ele não deve ser confiável para tarefas criptográficas futuras.)
Existem também situações em que é necessário invalidar um certificado antes da sua data de expiração, como quando o titular do certificado termina o contrato de trabalho com a empresa ou suspeita que a chave privada correspondente do certificado foi comprometida. Isso é chamado de revogação. Um certificado revogado é muito mais suspeito do que um certificado expirado. Os certificados expirados são inutilizáveis, mas não apresentam a mesma ameaça de comprometimento que um certificado revogado. Qualquer pessoa que tenha assinado um certificado pode revogar a sua assinatura no certificado (desde que utilize a mesma chave privada que criou a assinatura). Uma assinatura revogada indica que o signatário não acredita mais que a chave pública e as informações de identificação pertencem uma à outra, ou que a chave pública do certificado (ou a chave privada correspondente) foi comprometida. Uma assinatura revogada deve ter quase tanto peso quanto um certificado revogado. Com certificados X.509, uma assinatura revogada é praticamente igual a um certificado revogado, visto que a única assinatura no certificado é aquela que o tornou válido em primeiro lugar – a assinatura da CA. Os certificados PGP fornecem o recurso adicional de que você pode revogar todo o seu certificado (não apenas as assinaturas nele) se você achar que o certificado foi comprometido. Somente o proprietário do certificado (o detentor da chave privada correspondente) ou alguém que o proprietário do certificado tenha designado como revogador pode revogar um certificado PGP. (Designar um revogador é uma prática útil, pois muitas vezes é a perda da senha da chave privada correspondente do certificado que leva um usuário PGP a revogar seu certificado - uma tarefa que só é possível se alguém tiver acesso à chave privada. ) Somente o emissor do certificado pode revogar um certificado X.509.
Comunicar que um certificado foi revogado.
Quando um certificado é revogado, é importante conscientizar os usuários potenciais do certificado de que ele não é mais válido. Com certificados PGP, a maneira mais comum de comunicar que um certificado foi revogado é publicá-lo em um servidor de certificados para que outras pessoas que desejem se comunicar com você sejam avisadas para não usar essa chave pública. Em um ambiente PKI, a comunicação de certificados revogados é mais comumente obtida por meio de uma estrutura de dados chamada Lista de Revogação de Certificados, ou CRL, que é publicada pela CA. A CRL contém uma lista validada com carimbo de data e hora de todos os certificados revogados e não expirados no sistema. Os certificados revogados permanecem na lista apenas até expirarem e, em seguida, são removidos da lista — isso evita que a lista fique muito longa. A CA distribui a CRL aos usuários em algum intervalo programado regularmente (e potencialmente fora do ciclo, sempre que um certificado é revogado). Teoricamente, isso impedirá que os usuários usem involuntariamente um certificado comprometido. É possível, no entanto, que haja um período de tempo entre as CRLs em que um certificado recentemente comprometido seja usado.
O que é uma senha?
A maioria das pessoas está familiarizada com a restrição de acesso a sistemas de computador por meio de uma senha, que é uma sequência única de caracteres que um usuário digita como código de identificação.
Uma senha longa é uma versão mais longa de uma senha e, em teoria, mais segura. Normalmente composta por várias palavras, uma frase secreta é mais segura contra ataques de dicionário padrão, em que o invasor tenta todas as palavras do dicionário na tentativa de determinar sua senha. As melhores senhas são relativamente longas e complexas e contêm uma combinação de letras maiúsculas e minúsculas, caracteres numéricos e de pontuação. O PGP usa uma senha para criptografar sua chave privada em sua máquina. Sua chave privada é criptografada em seu disco usando um hash de sua senha como chave secreta. Você usa a senha para descriptografar e usar sua chave privada. Uma senha deve ser difícil de esquecer e difícil de ser adivinhada por outras pessoas. Deve ser algo já firmemente enraizado na sua memória de longo prazo, em vez de algo que você invente do zero. Por que? Porque se você esquecer sua senha, você estará sem sorte. Sua chave privada é total e absolutamente inútil sem sua senha e nada pode ser feito a respeito. Lembra-se da citação anterior neste capítulo?
 PGP é a criptografia que manterá os principais governos fora dos seus arquivos. Certamente também o manterá fora de seus arquivos. Tenha isso em mente quando decidir alterar sua senha para a piada daquela piada que você nunca consegue lembrar.
PGP é a criptografia que manterá os principais governos fora dos seus arquivos. Certamente também o manterá fora de seus arquivos. Tenha isso em mente quando decidir alterar sua senha para a piada daquela piada que você nunca consegue lembrar.Divisão de chave.
Dizem que um segredo não é segredo se for conhecido por mais de uma pessoa. Compartilhar um par de chaves privadas representa um grande problema. Embora não seja uma prática recomendada, às vezes é necessário compartilhar um par de chaves privadas. Chaves de assinatura corporativa, por exemplo, são chaves privadas usadas por uma empresa para assinar – por exemplo – documentos legais, informações pessoais confidenciais ou comunicados de imprensa para autenticar sua origem. Nesse caso, vale a pena que vários membros da empresa tenham acesso à chave privada. No entanto, isto significa que qualquer indivíduo pode agir plenamente em nome da empresa. Nesse caso, é aconselhável dividir a chave entre várias pessoas, de modo que mais de uma ou duas pessoas apresentem um pedaço da chave para reconstituí-la em condições utilizáveis. Se poucas peças da chave estiverem disponíveis, a chave ficará inutilizável. Alguns exemplos são dividir uma chave em três partes e exigir duas delas para reconstituir a chave, ou dividi-la em duas partes e exigir ambas as peças. Se uma conexão de rede segura for usada durante o processo de reconstituição, os acionistas da chave não precisam estar fisicamente presentes para aderirem novamente à chave.
-
 @ 502ab02a:a2860397
2025-05-02 03:05:18
@ 502ab02a:a2860397
2025-05-02 03:05:18เราได้อ่านเรื่อง EVERY eggwhite ไปแล้วคิดว่าเขาจะหยุดแค่นี้ไหมครับ 555555 ไม่มีทางครับ การคืบคลานต้องมีต่อไป วันนี้จะมาในตอนที่ชื่อว่า
EVERY Egg ไข่ยุคใหม่ที่ไม่ต้องใช้แม่ไก่อีกต่อไป ลองนึกภาพ "ไข่เจียว" ที่ไม่มีแม่ไก่เกี่ยวข้องแม้แต่ขนไก่สักเส้น...ใช่เลยจ้ะ โลกตอนนี้ไปถึงจุดที่ ไข่ สามารถผลิตได้จาก “ยีสต์” ที่ถูกดัดแปลงพันธุกรรม เพื่อให้มันสร้าง “โปรตีนไข่” แบบเดียวกับในธรรมชาติ โดยไม่ต้องผ่านแม่ไก่ ไม่ต้องมีเปลือก และแน่นอน...ไม่มีเสียงขันตอนเช้าอีกต่อไป
ผู้เล่นที่น่าจับตาที่สุดคือบริษัท EVERY Company จาก Silicon Valley เจ้าเดิมที่เปิดตัวผลิตภัณฑ์ใหม่ในชื่อ EVERY Egg ซึ่งเป็น “ของเหลว” ที่หน้าตาเหมือนวิปไข่ไก่ แต่เบื้องหลังคือกระบวนการผลิตระดับไซไฟ! พวกเขาใช้เทคนิคที่เรียกว่า precision fermentation หรือ “การหมักแม่นยำ” เพื่อสั่งให้ยีสต์สร้างโปรตีน ovalbumin (โปรตีนหลักในไข่ขาว) และ lysozyme (สารฆ่าเชื้อแบคทีเรียตามธรรมชาติในไข่) ออกมา จากนั้นก็เอามาผสม เติมแต่ง แต่งกลิ่น เติมสี ใส่สารกันเสียเล็กน้อย...ปิ๊ง! ได้ไข่ที่ไม่มีไข่ ได้ใจประชาชนที่กินสารอาหารแบบคลั่งตัวเลข
จุดขายที่ EVERY Company ใช้ในการนำเสนอ EVERY Egg สลุตมาเป็นตับ ตับ ตับ แบบนี้ครับ 1. High quality egg protein ใช้โปรตีน ovalbumin ที่ได้จากกระบวนการ fermentation ด้วย precision fermentation จากยีสต์สายพันธุ์ Pichia pastoris ซึ่งเป็น โปรตีนหลักในไข่ขาวธรรมชาติและเคลมว่าให้คุณสมบัติเทียบเท่าหรือดีกว่าไข่จากไก่ในเรื่องโครงสร้างโปรตีนและการทำงานในอาหาร เช่น การตีขึ้นฟู (foaming) และการอิมัลซิไฟ คุณเอ๊ยยยย ฟลัฟฟลี่สุดๆ 555 2. No hens used เป็น selling point หลักที่สื่อสารหนักมากในเชิง “ไม่เบียดเบียนสัตว์” ดูมีคุณธรรม จึงถูกจัดเป็นมังสวิรัติ (vegan-friendly) แม้จะได้จากจุลินทรีย์ที่ออกแบบให้ผลิตโปรตีนที่เหมือนจากสัตว์ จุดนี้ล่อใจผู้บริโภควีแกนและกลุ่มที่ต่อต้านฟาร์มอุตสาหกรรมอย่างเต็มๆ พร้อมถวิลหา 3. No cholesterol ยังเป็นจุดขายหลักได้ตลอดกาลกับการครอบงำให้กลัวคอเลสเตอรอล เพราะผลิตจากจุลินทรีย์ ไม่ใช่จากสัตว์จริง ๆ จึงไม่มีคอเลสเตอรอลเลย ซึ่งเป็นข้อได้เปรียบเทียบกับไข่ไก่ที่มีคอเลสเตอรอลตามธรรมชาติ 4. No saturated fat พอๆกันครับ ยังเป็นจุดขู่จุดขายได้ตลอดกาลเช่นเดียวกับคอเลสเตอรอล โปรตีนที่ผลิตจากยีสต์ไม่มีไขมันอิ่มตัวเช่นเดียวกับผลิตภัณฑ์จากสัตว์จริง 5. No artificial flavors แหม่ พยายามสร้างภาพลักษณ์ว่าเป็น clean label ไม่ใช้แต่งกลิ่นหรือสารเติมแต่งรส (แม้จะเป็นผลิตภัณฑ์ที่ผ่านกระบวนการขั้นสูงมากก็ตาม) 6. No salmonella จุดที่คนโคตรกลัวเลยในไข่ สังเกตุไหมว่า จัดหนักจัดเน้นขยี้ความกลัวของคนได้ทุกจุด อย่างอันนี้เนื่องจากไม่มีสัตว์เข้ามาเกี่ยวข้องในการผลิต ทำให้โอกาสปนเปื้อนเชื้อซัลโมเนลลาที่พบบ่อยในไข่สดแทบเป็นศูนย์ เป็นจุดขายด้านความปลอดภัยอาหาร (food safety) ที่เขาเน้นมาก
เท่านี้ยังไม่พอครับ คำถามที่คนต้องสงสัยแน่นอนคือ ชนิดของกรดอมิโนหละครบไหม pain point ของชาววีแกน เนื่องจาก EVERY Company ใช้เทคนิค “Precision Fermentation” โดยใส่ยีนจากไก่ลงไปในยีสต์ เพื่อให้ผลิต ovalbumin ได้เหมือนในธรรมชาติ จึงทำให้โครงสร้างของกรดอะมิโนในโปรตีนนี้ เหมือนไข่จริงแทบ 100% โปรตีน ovalbumin ที่ใช้ผลิต เป็น primary protein จึงถือว่าเป็น โปรตีนมาตรฐาน (reference protein) ในทางโภชนาการ เพราะมี กรดอะมิโนจำเป็นทั้ง 9 ชนิด ในปริมาณที่เพียงพอ ได้แก่ Leucine, Lysine, Valine, Isoleucine, Threonine, Methionine, Phenylalanine, Tryptophan, Histidine
แต่... แม้จะมีกรดอะมิโนครบ ก็ยังมีเรื่องให้คิด โปรตีนนี้ ไม่มาจากธรรมชาติ โดยตรง แต่ผ่านการผลิตจากสิ่งมีชีวิตดัดแปลงพันธุกรรม (GMO yeast) ยังไม่มีข้อมูลชัดเจนเรื่อง bioavailability (การดูดซึม) เมื่อเทียบกับไข่จริง และที่สำคัญ คือการบริโภค “complete protein” ไม่ได้แปลว่า ปลอดภัยในระยะยาว ถ้าพื้นฐานมันคือ GMO จากแลปที่ไม่มีวิวัฒนาการร่วมกับมนุษย์ แน่นอนว่ามันยังต้องการ "ตลาดทดลอง" เพื่อทดลองและเก็บข้อมูลประกอบสินค้าในระยะเวลานึง เข้าใจไหม "หนูๆ"
คำถามคือ โปรตีนแท้...หรือแค่ “เลียนแบบ” EVERY Egg บอกว่าเขาสร้างโปรตีนเหมือนไข่เป๊ะชนิดที่ว่าเชฟชื่อดังยังแยกไม่ออก (ถ้าไม่ดูฉลาก) สามารถนำไปทอด ทำไข่คน ไข่เจียว โอ๊มเล็ต ได้เหมือนไข่จริงทุกประการ แถมยังไม่มีคอเลสเตอรอล ไม่มีไขมันอิ่มตัว มีแต่ “โปรตีนล้วนๆ” แบบคลีนๆ
แต่ตรงนี้แหละที่มันเริ่ม น่าสงสัย เพราะการไม่มีไขมันเลย มันก็คือการตัดเอา matrix ทางโภชนาการ ที่ธรรมชาติออกแบบมาให้เราย่อยง่าย ดูดซึมวิตามินได้ดี และช่วยให้เรารู้สึกอิ่มแบบธรรมชาติ ไข่แท้จากไก่ ไม่ใช่แค่แหล่งโปรตีน แต่มันคือ “ของขวัญจากธรรมชาติ” ที่มีทั้ง choline, lutein, zeaxanthin, วิตามิน A, D, E, B12, โอเมก้า-3, ไขมันดี และเลซิธิน อยู่ครบทุกอนู ช่วยทั้งสมอง ดวงตา และตับ
ในขณะที่ EVERY Egg คือ “ไข่ที่เราอยากให้มันเป็น” มากกว่า “ไข่ที่ธรรมชาติอยากให้เราได้กิน”
บริษัท The EVERY Company ได้ร่วมมือกับเชฟระดับสุดยอดมากมาย ซึ่งการร่วมมือครั้งนี้มีเป้าหมายเพื่อแสดงให้เห็นว่าโปรตีนไข่ที่ผลิตจากกระบวนการ precision fermentation ของ EVERY Egg สามารถตอบสนองมาตรฐานสูงสุดของวงการอาหารชั้นเลิศได้ เรามาดูตัวอย่างกันครับว่า มีที่ไหนบ้าง
-
Eleven Madison Park โดย เชฟ Daniel Humm (มิชลิน3 ดาว ที่นิวยอร์ก) EVERY Egg เปิดตัวครั้งแรกในปี 2023 ที่ร้าน Eleven Madison Park ซึ่งเป็นร้านอาหารระดับมิชลิน 3 ดาว ในนิวยอร์ก โดยเชฟ Daniel Humm ได้สร้างสรรค์เมนูพิเศษที่ใช้ EVERY Egg เป็นส่วนประกอบหลัก เช่น ออมเล็ต ค็อกเทล และของหวาน เพื่อแสดงถึงความสามารถของผลิตภัณฑ์นี้ในการตอบสนองมาตรฐานสูงสุดของวงการอาหารชั้นเลิศระดับ fine dining มิชลิน
-
Chantal Guillon (ร้านมาการองฝรั่งเศสในซานฟรานซิสโก) EVERY Company ได้ร่วมมือกับร้านขนม Chantal Guillon ในการผลิตมาการองที่ใช้ EVERY EggWhite™ ซึ่งเป็นโปรตีนไข่ขาวที่ผลิตจากกระบวนการ precision fermentation โดยไม่มีการใช้ไข่จากไก่เลย ผลิตภัณฑ์นี้ได้รับการยอมรับว่าให้รสชาติและเนื้อสัมผัสที่เทียบเท่ากับไข่ขาวธรรมชาติ
-
The Vegetarian Butcher เป็นแบรนด์ในเครือ Unilever ตามที่ได้เคยให้ข้อมูลไปแล้ว EVERY Company ได้จับมือกับ The Vegetarian Butcher ซึ่งเป็นแบรนด์อาหารมังสวิรัติในเครือ Unilever เพื่อพัฒนาและผลิตผลิตภัณฑ์ที่ใช้โปรตีนไข่จาก EVERY Egg โดยมีเป้าหมายในการลดการใช้สัตว์ในห่วงโซ่อาหารและส่งเสริมความยั่งยืนในอุตสาหกรรมอาหาร
-
Grupo Palacios ผู้ผลิต Spanish Omelet รายใหญ่ของโลก EVERY Company ได้ร่วมมือกับ Grupo Palacios ซึ่งเป็นผู้ผลิต Spanish Omelet รายใหญ่ของโลก โดยนำ EVERY Egg มาใช้ในผลิตภัณฑ์ของตน เพื่อเป็นทางเลือกที่ปลอดภัยและยั่งยืนต่อไข่ไก่ธรรมชาติ ซึ่งอาจมีปัญหาเรื่องการปนเปื้อนและความไม่แน่นอนในการผลิต
Fiat Egg บนเส้นทางเดียวกับ Fiat Food เฮียชวนให้มองภาพใหญ่เหมือนเวลาเรายืนอยู่บนดาดฟ้าแล้วมองลงไปที่ตลาด... ผลิตภัณฑ์อย่าง EVERY Egg ไม่ใช่แค่การสร้าง “ของใหม่” แต่มันคือการ เปลี่ยนแปลงพื้นฐานของอาหาร ด้วยแนวคิดแบบ “Fiat” เป๊ะ Fiat Food คืออาหารที่ไม่ได้เกิดจากธรรมชาติ แต่ถูก “กำหนดให้มีคุณค่า” โดยอุตสาหกรรม Fiat Money คือเงินที่ไม่ได้มีมูลค่าในตัวเอง แต่รัฐบาลบอกให้เรายอมรับมันเป็นเงิน
ในโลกนี้ ถ้า “ไข่” ไม่ต้องมาจากแม่ไก่ “นม” ไม่ต้องมาจากเต้า และ “เนื้อ” ไม่ต้องมาจากวัว แต่ใช้แค่สารเคมี + ยีสต์ + กราฟ + กลิ่นสังเคราะห์ = “ของกินได้” แล้วมันจะเหลือความเป็น อาหารแท้ (real food) อยู่อีกไหม?
เบื้องหลังที่เราควรถามให้ลึก แม้ว่า EVERY จะอ้างว่าโปรตีนจากยีสต์ของเขา “ปลอดภัยและยั่งยืน” แต่ยังไม่มีข้อมูลด้าน long-term health impact ยังไม่มีข้อมูลว่ายีสต์ GMO ที่ใช้ จะกระตุ้นภูมิแพ้หรือมีสารตกค้างหรือไม่ ยังไม่รู้ว่าสารแต่งกลิ่น รส และตัวพาอื่นๆ ที่ใส่ใน EVERY Egg จะส่งผลอะไรกับ microbiome หรือฮอร์โมนของเราในระยะยาว แต่นั่นก็คงมาพร้อมกับคำตอบหรูๆหล่อๆว่า "ขอให้มั่นใจในกระบวนการผลิตที่ทันสมัยและดีเยี่ยม" . . . ตามเคย
และที่น่าสนใจคือ...ผลิตภัณฑ์ EVERY Egg ยังไม่ได้รับการรับรอง GRAS (Generally Recognized As Safe) อย่างเป็นทางการจาก FDA จึงยังไม่สามารถวางจำหน่ายในร้านค้าปลีกทั่วไปได้ บริษัทกำลังร่วมมือกับบริษัทอาหารข้ามชาติในการเปิดตัวผลิตภัณฑ์ในปีนี้ แต่ยังไม่มีข้อมูลชัดเจนเกี่ยวกับการวางจำหน่ายในร้านค้าปลีกทั่วไป แต่ส่วนตัวเฮียคิดว่าไม่น่ากังวล น่าจะผ่านฉลุยแหละ 5555
ไข่สังเคราะห์ = ความหวัง? หรือกับดักในรูปของนวัตกรรม? เราคงไม่ปฏิเสธว่ามีหลายคนบนโลกที่แพ้ไข่จริง หรือห่วงใยเรื่องสวัสดิภาพสัตว์ รวมถึงต้องการความ "บริสุทธิ์" "สกัด" "เข้มข้น" แต่คำถามคือ...จะดีกว่าไหมถ้าเราหาทางผลิต ไข่จริงจากไก่ที่เลี้ยงแบบธรรมชาติ ในระบบ regenerative farming แทนที่จะพยายามสร้างโปรตีนปลอมขึ้นมาแข่ง? ทุกครั้งที่มีของใหม่ที่ดูดี สะอาด และ “คลีน” เฮียอยากให้ทุกคน ถามกลับในใจว่า “คลีน” แค่ในห้องแล็บ หรือ “คลีน” ในธรรมชาติจริงๆ?
สรุปแบบไม่ต้องตีลังกาคิดได้ว่า EVERY Egg คือก้าวใหม่ของเทคโนโลยีอาหารที่กำลังวิ่งไปข้างหน้าแบบไม่เหลียวหลัง แต่ในฐานะที่เฮียเชื่อใน real food, nutrient density และความฉลาดของธรรมชาติ เราอาจต้องเตือนใจไว้ว่า...การใช้ยีสต์ดัดแปลงพันธุกรรมมาผลิต “ไข่เทียม” ไม่ใช่ความผิด แต่ก็ไม่ใช่ความจำเป็นไหม เพราะแท้จริงแล้ว เรามี “ไข่” ที่สมบูรณ์แบบอยู่ในธรรมชาติแล้ว...แค่ไม่ควรปล่อยให้อุตสาหกรรมทำลายภาพลักษณ์ของมัน เพื่อขายของที่ “เหมือนไข่” แต่ไม่มีชีวิต
คำถามเดิมครับ วันนึงเมื่อถึงจุดที่คุณไม่ได้เลือก แล้วมันมีให้แค่นี้ วันนั้นจะทำอย่างไร วันแห่งความ "บริสุทธิ์" "สกัด" "เข้มข้น" ที่เราถวิลหา ??? #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
-
 @ f683e870:557f5ef2
2025-04-28 10:10:55
@ f683e870:557f5ef2
2025-04-28 10:10:55Spam is the single biggest problem in decentralized networks. Jameson Lopp, co-founder of Casa and OG bitcoiner, has written a brilliant article on the death of decentralized email that paints a vivid picture of what went wrong—and how an originally decentralized protocol was completely captured. The cause? Spam.
The same fate may happen to Nostr, because posting a note is fundamentally cheap. Payments, and to some extent Proof of Work, certainly have their role in fighting spam, but they introduce friction, which doesn’t work everywhere. In particular, they can’t solve every economic problem.\ Take free trials, for example. There is a reason why 99% of companies offer them. Sure, you waste resources on users who don’t convert, but it’s a calculated cost, a marketing expense. Also, some services can’t or don’t want to monetize directly. They offer something for free and monetize elsewhere.
So how do you offer a free trial or giveaway in a hostile decentralized network? Or even, how do you decide which notes to accept on your relay?
At first glance, these may seem like unrelated questions—but they’re not. Generally speaking, these are situations where you have a finite budget, and you want to use it well. You want more of what you value — and less of what you don’t (spam).
Reputation is a powerful shortcut when direct evaluation isn’t practical. It’s hard to earn, easy to lose — and that’s exactly what makes it valuable.\ Can a reputable user do bad things? Absolutely. But it’s much less likely, and that’s the point. Heuristics are always imperfect, just like the world we live in.
The legacy Web relies heavily on email-based reputation. If you’ve ever tried to log in with a temporary email, you know what I’m talking about. It just doesn’t work anymore. The problem, as Lopp explains, is that these systems are highly centralized, opaque, and require constant manual intervention.\ They also suck. They put annoying roadblocks between the world and your product, often frustrating the very users you’re trying to convert.
At Vertex, we take a different approach.\ We transparently analyze Nostr’s open social graph to help companies fight spam while improving the UX for their users. But we don’t take away your agency—we just do the math. You take the decision of what algorithm and criteria to use.
Think of us as a signal provider, not an authority.\ You define what reputation means for your use case. Want to rank by global influence? Local or personalized? You’re in control. We give you actionable and transparent analytics so you can build sharper filters, better user experiences, and more resilient systems. That’s how we fight spam, without sacrificing decentralization.
Are you looking to add Web of Trust capabilities to your app or project?\ Take a look at our website or send a DM to Pip.
-
 @ 3eba5ef4:751f23ae
2025-05-02 02:10:09
@ 3eba5ef4:751f23ae
2025-05-02 02:10:09加密洞见
secp256k1lab:一个不安全的 Python 库,如何让比特币更安全
一些比特币开发者长期以来一直认为应该有一个统一的、可重用的加密 BIP 参考 secp256k1 代码标准。Blockstream 研究团队发布了 secp256k1lab (GitHub Repo)—— 一个新的、故意不安全的 Python 库,用于原型开发、实验和 BIP 规范的制定。
该库并不用于生产的(因为没有常数时间防护,因此易受侧道攻击),但填补了一个空白:提供了一个干净且一致的 secp256k1 功能参考实现,包括 BIP-340 风格的 Schnorr 签名、ECDH 以及底层的域/群运算。该库的目标是:通过避免重复的、一次性的实现,让未来编写 BIP 变得更简单、更安全。对于 BIP 作者来说,这意味着更少的自定义代码和规范问题,以及一条更清晰的从原型到正式提案的路径。
使用基于时间的一次性密码(TOTP)在软件钱包中进行密码验证和访问控制
本文介绍了一种在比特币软件钱包中,使用基于区块的时间同步一次性密码(TOTP, Time-based One-Time Password)机制进行密码验证和钱包访问控制的方法。 与传统的 TOTP 系统不同,这种方法将区块链数据——特别是比特币的区块高度和区块哈希 ——同一个安全存储的加密信息结合,来生成一个动态变化的 6 位数验证码,具备以下安全属性:
-
双重保护:结合了设备持有性和基于区块链衍生的、基于时间的数据(blockchain-derived time-based data)。
-
抗重放攻击:验证码随每个新区块(约 10 分钟一个周期)更新。
-
最小攻击面:无需输入或复制密码短语。
-
硬件加密保护秘密信息:移动端应用的秘密信息存储在不可导出的安全硬件中。
比特币特征矩阵:跟踪比特币产品/服务的互操作性
Bitcoin Opentech 在此页汇集并跟踪比特币相关产品/服务的互操作性。
汇集各种比特币软分叉提案的网站
bitcoin.softforks.org 网站汇集了各种比特币软分叉提案,包含组件、实现原语等关键软分叉信息,以及使用该分叉的使用案例和用户等。
以太坊社区热议 RISC-V 替代 EVM,CKB-VM 经验倍受关注
Vitalik 近日在 Ethereum 的论坛上提出了将用 RISC‑V 代替 EVM 的设想,并提到 CKB-VM 的设计作为参考范例,引发了两个社区对 RISC-V 技术决策的关注和探讨。随着讨论的展开,CKB-VM 当年的设计考量又重新被提起,并吸引了更多人回顾和学习相关经验。CKB 是 Nervos Network 的 Layer 1 公链,其支持智能合约的 Cell 模型受比特币 UTXO 模型启发,并使用基于 RISC-V 的 CKB-VM 虚拟机,实现高效且支持多语言的合约执行。了解更多 CKB-VM 详情:
在 Ark 中集成 Taproot Assets 的概念验证
Ark Labs 分享了如何将 Taproot 资产集成到 Ark 的链下批处理层中:在 Ark 标准交易流程上,引入了 tVTXO(tokenized Virtual Transaction Output)——嵌入 Taproot 资产承诺的虚拟输出。tVTXO 的行为与任何其他 VTXO 一样,可在 Ark 的链下层花费,可预先签名以实现单边退出,但它包括两个关键附加功能:
-
资产承诺(Asset Commitments):使用 Taproot 的内部密钥和 TapTree 结构嵌入到 PkScript 中。
-
传输证明文件(Transfer Proof Files)是一条加密见证的确定性链,通过链下树跟踪资产的包含路径。这些证明可以通过链上元数据激活,从而退出 Taproot Asset 生态。
Erk:改进 Ark 协议,无需用户轮次交互
Erk 是 Ark 协议的一种新颖变体,引入了具有可重新绑定签名的「退款交易」(refund transactions),允许用户提前提供可应用于未来输出的签名。然后,服务器可以安全地刷新 VTXO,而无需用户在每一轮都处于联机状态。这解决了 Ark 的关键限制之一——要求用户在 VTXO 到期之前上线。
Erk 的另一个强大功能是「永久离线刷新」——用户可以按顺序批量预签名未来的刷新。通过 watchtower 监控协议,用户可以在资金保持安全的情况下无限期地保持离线状态。
Robosats:无 KYC 闪电网络 P2P 交易,支持人民币通过微信交易
RoboSats 是一个无 KYC 的开源闪电网络交易平台,使用LN Hodl invoices 最大限度地减少托管和信任要求。用户通过 Tor 浏览器操作,体验简单且交易费用低廉的 P2P 交易。
平台目前也支持通过微信进行人民币。
值得关注的几个闪电网络基础设施项目
OpenSats 的这篇文章重点关注闪电网络在基础设施上的推进,提到以下项目:
-
Lighting Splicing: 允许用户在不停机的情况下动态调整通道容量。通过消除关闭和重新打开通道的需要,Splicing 即减少了摩擦和成本,又简化了流动性管理。
-
Validating Lightning Signer (VLS): 通过将密钥存储和交易验证转移给外部签名者,来解决闪电网络传统的、将私钥直接存储在节点上用于交易签名的方式的风险,从而确保即使闪电节点遭到入侵,攻击者也无法访问或滥用私钥来窃取资金。
-
BLAST (Big Lightning Automated Simulation Tool): 目标是为闪电网络提供稳定的建模和仿真框架,为研究和开发人员和节点运营商提供更准确地反映真实网络状况的大规模测试环境。
-
Lampo: 提供了一个基于 Lightning 开发工具包(LDK)构建的模块化、社区驱动的开发工具和节点实现方案。
-
Lnprototest: 提供了一个基于 Python 的测试库,可帮助开发人员验证不同实现中的协议合规性,确保交叉兼容性并防止回归,以免影响实际用户。
Citrea 推出基于 BitVM 的信任最小化双向挂钩桥 Clementine
Rollup 项目 Citrea 在比特币测试网上部署了 Clementine Bridge,这是比特币测试网上第一个完整的 BitVM 桥设计。Clementine 桥是 Citrea 基于 BitVM 的信任最小化双向挂钩方案,核心组件包括:
-
比特币和 Citrea 的轻客户端证明
-
BitVM 中的零知识证明验证器
只要 BitVM 设置中的单个验证器是诚实的,Clementine 就会保持安全。这是对现有解决方案(开放和封闭联合)的重大改进。Clementine 桥的设计和 Citrea 的去信任轻客户端一起,最大限度减少了对 Citrea 双向挂钩的信任要求,且无需软分叉。
详情可参考 Clementine 白皮书,以及特征简介。
RISC-V 成为 BitVMX 验证系统最佳选择的五个关键原因
作为 BitVMX 的主要开发者的 Fairgate Labs 概述了 RISC-V 成为 BitVMX 验证系统最佳选择的五大关键:
-
开放且通用:RISC-V 作为标准,无 IP 障碍
-
成熟的工具支持:编译器和调试器的丰富生态系统
-
操作码简单
-
支持高级语言
-
支持通用验证
精彩无限,不止于链
违规却挡不住需求:深圳的 LuckyMiner 在争议中推动家用小型矿机普及
LuckyMiner 是一家深圳的比特币挖矿初创公司,它们生产家用迷你矿机正越来越受欢迎。LuckyMiner 模仿的主要对象是美国产的开源的小型矿机 Bitaxe。虽然开源,但 Bitaxe 适用于 CERN-OHL-S-2.0 规则,要求任何修改都需公开,而 LuckyMiner 并未遵循此规则。
这条推文的发帖人称跟 LuckyMiner 的创始人吃了饭,后者并不遮掩 LuckyMiner 违反了许可,并表示,除了零售的 LuckyMiner 之外,它们也为 B 端客户生产符合开源许可的 Bitaxes,并且同时仿造 braiins 的挖矿设备。
在对负担得起的家用采矿设备的需求不断增长的推动下,LuckyMiner 已经取得了成功。虽然存在争议,但低成本矿工的崛起表明草根阶层对比特币感兴趣,尤其是在亚洲努力应对日益增长的威权主义和金融压迫的时候。
反对销毁受易量子攻击的比特币
关于如何处理易受攻击的地址里的比特币,Jameson Lopp 在此前的文章中,表示它反对恢复这些代币,并主张原地销毁,以防止资金被量子计算的获胜者拿走。
而 UTXO Management 的 Guillaume Girard 在此反驳了 Lopp 的主张,出于以下考虑:
-
侵犯财产权:未经持有者同意就销毁这些币,违反了财产权原则。强制让这些币不可使用,破坏了比特币中对所有权和控制权的基本尊重
-
伦理问题:尽管销毁易受攻击的币是为了防止未来量子攻击者盗币,但实际上也会无差别地惩罚那些遗失钱包或不了解量子威胁的用户。这种做法在伦理上存在严重问题,因为不给用户自救的机会。
他提出了一些更具建设性的替代方案来取代销毁策略:
- Hourglass(沙漏机制):旨在减轻“没收式销毁”和“市场抛售”这两种方式带来的负面影响。它通过限制量子攻击事件可能引发的供应冲击,既不烧毁币,也不导致市场被抛压所淹没。
这一方案由 Hunter Beast 提出,试图成为“破坏性最小”的解决方案,目前正在开发者社区中接受评估。此外,Hunter Beast 也已经提出了 BIP 360,以引入抗量子密码学(PQC)并新增一种比特币地址类型。
让旧矿机继续发挥余热:边挖矿边供暖的未来可能
BitMEX 对 Heatbit Trio 比特币挖矿加热器做了测评。该产品本质上是一个旧矿机,配备有一个安静的风扇,适用于房间供暖。
作者表示 Heatbit 的商业模式很吸引人,结合挖矿机和加热器的领域也值得长期关注。因为从长远来看,部分由于摩尔定律的物理限制,ASIC 效率的提高速度将下降,因此 ASIC 可以经济地开采比特币更长的时间(如 10 年)。随着涉及的新风险技术的减少,生产成本也应该会下降。当这种情况发生到足够程度时,将比特币挖矿与加热设备相结合可能是有意义的,例如,游泳池、商用锅炉、住宅锅炉以及商用和住宅电加热系统。
开放、即时和无国界支付:稳定币未来
a16z 的该报告探讨了稳定币会如何颠覆全球支付行业,以及谁将从中受益最大等问题。
作者将稳定币的到来称为赚钱的「WhatsApp 时刻」,因为它使国际交易几乎免费、即时、开放。此外,文章指出只有两种稳定币是被认可的:法币或资产支持的稳定币,而 「策略支持的合成美元 」(Strategy-backed synthetic dollars, SBSD)并不被承认是可靠的价值储存或交换媒介。
-
-
 @ 99556507:a6cf5c08
2025-05-02 09:19:37
@ 99556507:a6cf5c08
2025-05-02 09:19:37El paradigma del trabajador común aceptado en nuestra era es trabajar duro durante 40 años por un salario para tener derecho a una jubilación los últimos 20 o con suerte 25 años de vida.
Pero ¿es ésto lo más rentable? ¿Hay otras alternativas?
Vamos a ponernos en la piel de un asalariado o un autónomo que ha cotizado durante 30 años por la base máxima y está a una década todavía de poder jubilarse. ¿Le conviene trabajar esa década para tener derecho a la pensión estatal? ¿O es una estafa?
Hagamos números: La cotización máxima del autónomo o la del empresario a cuenta del trabajador hoy en día es de 1.472€/mes, 12 pagas al año, o 17.664€/año. En 10 años, y considerando una inflación del 4% anual, pagará 202.075€ en cotizaciones sociales.
El cotizante que haya pagado esto durante toda su vida laboral tiene derecho a la jubilación máxima, que hoy es de 3.267€/ mes, 14 pagas al año, o 45.746,40€/año. Si pensamos que la esperanza de vida en España es de 83 años y se tiene derecho a la jubilación a los 67, significa que un pensionista medio recibirá la pensión durante 16 años. Pero vamos a a hacer las cuentas para Matusalén, el pensionista pesadilla para el gobierno y las aseguradoras, que llegará a cumplir los 92 años, recibiendo la pensión durante 25 años.
Asumamos que el gobierno, que necesita imperiosamente los votos de los 7 millones de pensionistas, seguirá revalorizando las pensiones con el IPC oficial, es decir, a una media del 4% anual.
Matusalén se jubilará a los 67 y recibirá a lo largo de sus 25 años de pensionista la cantidad de 1.905.000€(1), de los cuales tendrá que pagar alrededor de un 28% de impuestos.
[(1) 45.746,40*(1-1,0425)/(1-1.04)] = 1.905.150
Es decir, Matusalén pagará 202.000€ en total a lo largo de 10 años para recibir 1.905.000€ distribuidos durante los siguientes 25. Parece un buen negocio, ¿no?
Pero, y si Matusalén, que es una persona cabal y ahorradora, ha ido haciendo una hucha durante sus 30 años de vida laboral a razón de 1000€ al mes, de manera que ahora ya dispone de esos 202.075€ necesarios para pagar sus cotizaciones hasta la edad de jubilación, y además le sobran 160.000€ para sus gastos la próxima década, a razón de 16.000€/año, que deberían de ser suficiente para vivir, puesto que esta cantidad es justo el salario mínimo interprofesional actual. ¿Le merece la pena seguir trabajando o puede plantearse dejar de hacerlo y usar esos ahorros para pagar sus cotizaciones de los siguientes 10 años, y tener derecho a la jubilación cuando cumpla 67 años?
O ya puestos a hacer cuentas, dado que tiene un capital disponible de 202.000€ en el banco, ¿podría pensar en alguna inversión alternativa que revalorizara su dinero de manera que mejorase las prestaciones de su jubilación (los 1.905.000€ calculados antes)?
Aquí es donde sale a jugar la fórmula del interés compuesto: Cf = Ci * (1+Rn), donde: Cf: capital final (queremos llegar a 1.905.000€) Ci: capital inicial (los 202.075€ de Matu) R: tasa de interés anual (CAGR) n: numero de años de la inversión (10)
¿Qué crecimiento anual compuesto (CAGR) necesitaría Matu para obtener el total de lo que nos daría su pensión tras 25 años, pero en tan solo 10 años, de manera que pudiera disponer de todo ese capital incluso antes de jubilarse? Haciendo las cuentas, R = (Cf/Ci-1)(1/n) = 23.09 %
Por si has llegado hasta aquí pero te has perdido por el camino, acabamos de concluir que una persona que invierta hoy 202.075€ en un producto que rente un 23,09% anual, obtendrá 1.905.000€ en 10 años, el equivalente a toda su jubilación.
Pues esto parece incluso mejor que la alternativa anterior, ¿no? Pero claro, hay que encontrar un producto que garantice esta rentabilidad sostenida durante una década. ¿Qué podría ser? A esta alturas, si sigues por aquí, ya habrás podido intuir por dónde van los tiros. Lo único que ha garantizado esta revalorización hasta la fecha es #bitcoin.
Éste el el cuadro del CAGR de Bitcoin tabulado por años. Se lee de la siguiente manera: A finales de 2024, la columna "CAGR 2024" da el CAGR (rendimiento anual compuesto) para la diferencia de años entre 2024 y el año de la cifra que estemos mirando. Por ejemplo, el CAGR a 31/12/2024 de una inversión realizada el 31/12/2023, es decir de 1 año, es del 276,92%. Si la inversión se realizó el 31/12/2016, el CAGR 8 años después, a final de 2024, es del 78,22% ANUAL
(Ver imagen 1)
El tío Matusalén está buscando algo que le dé un mínimo del 23,09% anual, ¿recordáis?. Pues da igual cuándo haya invertido y cuánto tiempo mantenga la inversión. BTC siempre supera ese umbral, por mucho.
"Ya Manolito, pero estás mirando rendimientos desde finales de 2024, cuando Bitcoin hizo un precio máximo histórico. Esto no asegura que haya ocurrido esto cada año, ¿no?"
El siguiente cuadro muestra los CAGR calculados a finales de cada año, los últimos 6 años. Las cifras en verde corresponden a los rendimientos de inversiones mantenidas 10 años. No podemos ir más para atrás porque Bitcoin acaba de cumplir 16 años.
(ver imagen 2)
No es difícil comprobar que a 10 años vista, bitcoin siempre ha superado de largo esta tasa de crecimiento.
*Consideraciones fiscales ** La pensión máxima devenga impuestos sobre la base de rentas del trabajo a razón del 28% anual, mientras que las inversiones tributan a un máximo del 26% sobre la base de las rentas de capital, suponiendo que se recupere todo el mismo año. Si se distribuyen los rendimientos plurianualmente, ese 26% puede reducirse entono al 21%, suponiendo otro 7% anual de ventaja neta sobre la pensión. En el caso particular de Matusalén, los 45.746,40€ anuales de su pensión tributarían íntegros al 28%, por lo que los 1.905.150 se quedarían netos en 823.435,20€ al cabo de 25 años. Si hubiese optado por invertir los 202.075€ en Bitcoin, y suponiendo que la rentabilidad obtenida es solo la necesaria para conseguir los 1.905.150€, tributaría al 26% sobre la ganancia si decide convertirlos en € de una vez, es decir, pagaría 26%(1.905.150-202.075)=442,800€, con lo que le quedarían netos 1.462.350€. Si decide por el contrario vender solo bitcoins cada año por valor de 45,746€, y suponiendo que mantienen el mismo valor en € durante los 25 años, pagaría el 21% sobre la plusvalía, es decir 357.645€ a lo largo de los 25 años por lo que le habrá quedado neto 1.547.504€.
Resumiendo: Renta neta con la pensión estatal tras 25 años: 823.435€ Renta neta con el plan de inversión en bitcoin, con rescate en una vez, el año 0: 1.462.350€ Renta neta con el plan de inversión en bitcoin, con rescate a lo largo de 25 años: 1.547.504€
Hay que recordar que todo el ejercicio está realizado para el mejor caso del pensionista estatal, que vivirá muy por encima de la media. Cualquier número de años inferior mejorará la rentabilidad del plan de bitcoin respecto al estatal.
Conclusión: Al bueno de Matu más le vale comprar bitcoins hoy mismo con ese dinero ahorrado. No solamente no necesitará una pensión sino que lo más probable es que sus ahorros valgan 5 veces más que lo que conseguiría de pensionista, pero 25 años antes.
-
 @ 6be5cc06:5259daf0
2025-04-28 01:05:49
@ 6be5cc06:5259daf0
2025-04-28 01:05:49Eu reconheço que Deus, e somente Deus, é o soberano legítimo sobre todas as coisas. Nenhum homem, nenhuma instituição, nenhum parlamento tem autoridade para usurpar aquilo que pertence ao Rei dos reis. O Estado moderno, com sua pretensão totalizante, é uma farsa blasfema diante do trono de Cristo. Não aceito outro senhor.
A Lei que me guia não é a ditada por burocratas, mas a gravada por Deus na própria natureza humana. A razão, quando iluminada pela fé, é suficiente para discernir o que é justo. Rejeito as leis arbitrárias que pretendem legitimar o roubo, o assassinato ou a escravidão em nome da ordem. A justiça não nasce do decreto, mas da verdade.
Acredito firmemente na propriedade privada como extensão da própria pessoa. Aquilo que é fruto do meu trabalho, da minha criatividade, da minha dedicação, dos dons a mim concedidos por Deus, pertence a mim por direito natural. Ninguém pode legitimamente tomar o que é meu sem meu consentimento. Todo imposto é uma agressão; toda expropriação, um roubo. Defendo a liberdade econômica não por idolatria ao mercado, mas porque a liberdade é condição necessária para a virtude.
Assumo o Princípio da Não Agressão como o mínimo ético que devo respeitar. Não iniciarei o uso da força contra ninguém, nem contra sua propriedade. Exijo o mesmo de todos. Mas sei que isso não basta. O PNA delimita o que não devo fazer — ele não me ensina o que devo ser. A liberdade exterior só é boa se houver liberdade interior. O mercado pode ser livre, mas se a alma estiver escravizada pelo vício, o colapso será inevitável.
Por isso, não me basta a ética negativa. Creio que uma sociedade justa precisa de valores positivos: honra, responsabilidade, compaixão, respeito, fidelidade à verdade. Sem isso, mesmo uma sociedade que respeite formalmente os direitos individuais apodrecerá por dentro. Um povo que ama o lucro, mas despreza a verdade, que celebra a liberdade mas esquece a justiça, está se preparando para ser dominado. Trocará um déspota visível por mil tiranias invisíveis — o hedonismo, o consumismo, a mentira, o medo.
Não aceito a falsa caridade feita com o dinheiro tomado à força. A verdadeira generosidade nasce do coração livre, não da coerção institucional. Obrigar alguém a ajudar o próximo destrói tanto a liberdade quanto a virtude. Só há mérito onde há escolha. A caridade que nasce do amor é redentora; a que nasce do fisco é propaganda.
O Estado moderno é um ídolo. Ele promete segurança, mas entrega servidão. Promete justiça, mas entrega privilégios. Disfarça a opressão com linguagem técnica, legal e democrática. Mas por trás de suas máscaras, vejo apenas a velha serpente. Um parasita que se alimenta do trabalho alheio e manipula consciências para se perpetuar.
Resistir não é apenas um direito, é um dever. Obedecer a Deus antes que aos homens — essa é a minha regra. O poder se volta contra a verdade, mas minha lealdade pertence a quem criou o céu e a terra. A tirania não se combate com outro tirano, mas com a desobediência firme e pacífica dos que amam a justiça.
Não acredito em utopias. Desejo uma ordem natural, orgânica, enraizada no voluntarismo. Uma sociedade que se construa de baixo para cima: a partir da família, da comunidade local, da tradição e da fé. Não quero uma máquina que planeje a vida alheia, mas um tecido de relações voluntárias onde a liberdade floresça à sombra da cruz.
Desejo, sim, o reinado social de Cristo. Não por imposição, mas por convicção. Que Ele reine nos corações, nas famílias, nas ruas e nos contratos. Que a fé guie a razão e a razão ilumine a vida. Que a liberdade seja meio para a santidade — não um fim em si. E que, livres do jugo do Leviatã, sejamos servos apenas do Senhor.
-
 @ fd0bcf8c:521f98c0
2025-05-02 02:02:13
@ fd0bcf8c:521f98c0
2025-05-02 02:02:13Bitcoin
It stands alone. Immutable. Unyielding. It records without mercy. Each transaction cuts deep. Some carry wealth. Others just data. The debate rages on.
OP_RETURN
It divides us all. Bloat versus freedom. Money versus use. Simple versus complex.
Nodes
They bear heavy weight. Each byte costs something. Storage grows. Bandwidth drains. Money defenders stand guard.
"Our purpose is clear...Money serves one master." —Mises
Not art.
Not storage.
Not games.
The fee-payers
They disagree. "I paid. I belong." The miners take their cut. The highest fee wins. No questions asked. The protocol allows it.
"Accept what exists."—Marcus Aurelius
The chain is neutral. Always neutral.
What is a transaction?
None agree. Value transfer only? Or any valid data? The white paper speaks. "Electronic cash system." Yet code evolved. It grew teeth. It allows more now.
"Shitcoin"
Cuts both ways. A dangerous word. It keeps focus. It maintains unity. But it wounds creation. Makes builders desperate. They force ideas onto Bitcoin. They use OP_RETURN poorly. They bloat what needs no bloating. Seneca saw this coming...
"Fear makes suffering worse."
Innovation needs proper soil. Not forced transplants.
Money debates sharpen knives. Is Bitcoin gold? Is it currency? Mantras echo loudly.
"Digital gold."
_"Spend dollars, saving Bitcoin." _
"Never sell your Bitcoin."
Bitcoin becomes idol. Not tool. Mises would disapprove, "Money must move." Without exchange, it dies. If none spend, why fight bloat?
Rhetoric
It hurts us. "Shitcoin" closes minds. Forces square pegs round. Drives experiments home. To Bitcoin they return. Bearing misshapen plans.
"Knowledge exists in dispersion," Hayek warns.
Let ideas find homes. Let Bitcoin be Bitcoin.
Fees
They bring new problems. Users flee high costs. They seek cheaper chains. The wealthy still play games. They can afford the bloat. The poor cannot compete. The rich inscribe at will. Rothbard saw this trap, "Markets need equal rules."
Fee markets favor wealth. Always have. Always will.
Nodes must still run. Validators must validate. Decentralized. Resistant. Strong. The burden grows heavier. But principles matter most.
The battle
It continues. Hard words. Hard choices.
Bitcoin endures all. Money or platform? Gold or currency? The answers shift. The chain grows. Block by block. Byte by byte.
We need clearer words. Cleaner definitions. Less pride. More thought. Let Bitcoin be what it is. Not what we demand.
Bitcoin is human.
Not magical. Not divine. Fallible like its makers. A young experiment still. It could fail tomorrow.
"Nothing is too big to fail." —Satoshi
Our rhetoric needs maturity. Our definitions need clarity. Bitcoin needs humility. From all who touch the code.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ b69b97fa:982d77f6
2025-05-02 01:58:50
@ b69b97fa:982d77f6
2025-05-02 01:58:50O livro de Gênesis, o primeiro da Bíblia, revela o início da história da criação e da redenção. A tradição reformada atribui a autoria humana de Gênesis a Moisés, inspirado por Deus. Escrito por volta de 1446–1406 a.C. enquanto o povo de Israel se preparava para entrar na terra prometida, Gênesis foi dado para “instruir os israelitas sobre o propósito de Deus para eles como nação” e mostrar como seus primórdios se ligam ao plano de salvação. Desde as primeiras linhas o texto enfoca a soberania divina: “Nas primeiras linhas de Gênesis…desdobra-se o poder e a autoridade divina na formação do mundo” . Esse pano de fundo inspirador abre o livro, preparando o coração do leitor para entender como Deus age desde o começo da criação até a aliança com os patriarcas.
Temas principais em Gênesis
-
Criação e soberania de Deus: Gênesis relata que “no princípio Deus criou os céus e a terra” (Gn 1:1) e apresenta o Senhor como Criador onipotente. A narrativa mostra que o mundo tem um propósito – Deus ordenado e bom – e que o homem é formado à imagem de Deus, conferindo ao ser humano dignidade única. Desde o início vemos que Deus é soberano sobre toda a história, como apontado em estudos bíblicos: “a narrativa da criação desdobra o poder e a autoridade divina na formação do mundo”.
-
A Queda do homem: Com Adão e Eva, o pecado entra no mundo (Gn 3). O texto registra que a desobediência rompeu a comunhão entre a humanidade e Deus, trazendo culpa, medo e sofrimento a todas as relações. A Bíblia explica que “o pecado introduz no mundo a culpa e o medo, marcas profundas” e provoca consequências como violência e separação de Deus. Essa queda fundamenta em Gênesis a doutrina do pecado original e explica por que o mundo ficou quebrado. Mas logo após a Queda Deus faz promessas redentoras – uma decepção de um começo ao mostrar também a graça que virá.
-
Aliança com o povo de Deus: Em Gênesis, Deus estabelece pactos importantes. Ao salvar Noé, Deus renova a criação e promete nunca mais destruir a terra com água (Gn 9), selando um arco-íris como sinal de aliança. Depois, chama Abraão e promete: “far-te-ei uma grande nação… em ti serão benditas todas as famílias da terra” (Gn 12:2–3). Essa promessa a Abraão – de que os descendentes dele seriam muitos e abençoariam o mundo – é o fundamento da aliança abraâmica. Nas palavras de estudiosos, “o conceito de aliança… começa com a promessa feita a Abraão, na qual Deus se compromete a fazer dele uma grande nação… abençoando-o e tornando-o uma bênção para todas as nações”. Assim, Gênesis mostra Deus escolhendo e guiando um povo através de acordos firmados por Sua graça.
-
Promessa do Redentor: Mesmo depois da Queda, Deus anuncia a salvação futura. Logo após a queda de Adão, Ele diz à serpente que fará inimizade entre a “semente da mulher” e a do inimigo, e que “essa lhe ferirá a cabeça” (Gn 3:15). Essa profecia inicial – chamada de protoevangelho – antecipa a vinda de um Redentor. Gênesis, portanto, já aponta a esperança de redenção: como interpretações reformadas explicam, Deus “revelou Seu pacto da graça… prometendo um Salvador (Gn.3:15), aquele que restauraria o reino recentemente destruído”. Esse fio vermelho continua na aliança com Abraão: a bênção prometida a ele (“em ti serão benditas todas as famílias da terra”) vislumbra a obra de Cristo para todas as nações. Em resumo, Gênesis apresenta a teia de criação, pecado e aliança na qual Deus já coloca as sementes de Sua salvação.
Cristo anunciado em Gênesis
Ao ler Gênesis à luz de Cristo, vemos vários anúncios e figuras do Messias:
- Protoevangelho (Gn 3:15): Logo depois da queda, Deus promete que a “semente da mulher” ferirá a cabeça da serpente. Essa é a primeira promessa de redenção bíblica . Ela estabelece “a expectativa de um Redentor, que seria um descendente… de Adão e Eva” . Em outras palavras, mesmo no Éden, Deus começava a revelar Seu plano de salvar o mundo. Ao longo da narrativa, essa semente se identifica com Cristo, que derrotaria o pecado e a morte.
- Promessa a Abraão: Deus disse a Abraão que “em tua descendência… seriam abençoadas todas as nações” (Gn 12:3). O Novo Testamento esclarece que essa “descendência” se refere a Cristo. Como ensina um comentário bíblico: “A ‘semente’ mencionada… refere-se à vinda do Redentor, que os cristãos identificam como Jesus Cristo. Em Gênesis 12 vemos a continuação da promessa do Redentor através da descendência de Abraão”. Assim, Jesus é o cumprimento da promessa dada a Abraão (cf. Gl 3:16).
-
Tipos de Cristo em Gênesis: Vários personagens e eventos de Gênesis prefiguram Jesus:
• José: Amado por seu pai, mas traído e vendido por prata, José sofre injustamente nas mãos dos irmãos. Depois é exaltado e acaba salvando muitas pessoas durante a fome. Esse paralelo com Jesus é marcante: Cristo era amado pelo Pai (Mateus 3:17), rejeitado pelo seu povo, traído por 30 moedas de prata, sofreu injustamente e acabou salvando o mundo do pecado. José é o tipo perfeito de “servo sofredor” que Deus exalta para trazer salvação.
• Abraão e Isaque: Abraão demonstrou fé ao aceitar sacrificar seu filho Isaque em obediência a Deus (Gn 22). Deus proveu um carneiro substituto no lugar de Isaque. Essa cena figura o grande sacrifício de Deus oferecendo Seu Filho como Cordeiro do pecado. Como nota um estudo, o quase-sacrifício de Isaque “simboliza o sacrifício de Deus com Jesus”.
• Adão e o “último Adão”: A Bíblia chama Jesus de o “último Adão” (1Co 15:45). Onde Adão trouxe morte (pelo pecado), Cristo traz vida eterna. A queda do primeiro homem abriu caminho à necessidade do Salvador; Cristo, o último Adão, repara o que foi quebrado. Este paralelo é mencionado em estudos bíblicos: “Adão: Jesus é chamado de o ‘último Adão’… pois trouxe vida onde Adão trouxe morte”.
Cada um desses elementos mostra que Gênesis não é apenas história antiga, mas um começo anunciado da obra de Cristo. Desde as promessas a Adão e Abraão até as figuras de José e Isaac, vemos Deus preparando o caminho para o Redentor.
Aplicações práticas para a vida cristã hoje
-
Fé e confiança em Deus: Gênesis exalta a fé dos patriarcas como exemplo para nós. Abraão é chamado de “pai da fé” porque creu nas promessas de Deus mesmo sem ver todos os detalhes. A Bíblia diz de Abraão: “Abrão creu no Senhor, e isso lhe foi creditado como justiça” (Gn 15:6). Esse acontecimento mostra que a justificação do cristão não vem de obras, mas de crer em Deus. Somos encorajados a confiar nas promessas divinas como Abraão fez – crer que Deus cumprirá o que prometeu, mesmo em meio à espera. Como observa um estudo, mesmo sem saber para onde Deus o levava, Abraão “obedeceu prontamente, demonstrando uma confiança inabalável no plano divino”. Em nossa vida, confiar em Deus sem ver o fim da história é um exercício de fé constante, inspirado pelo exemplo de Abraão.
-
Obediência e perseverança: Gênesis ensina que a verdadeira fé se manifesta na obediência. Ao ser chamado para uma terra desconhecida, Abraão saiu da sua terra por ordem de Deus. Ao quase sacrificar Isaque, ele mostrou obediência sem entender todos os detalhes. José, mesmo injustiçado, permaneceu íntegro no Egito e Deus o usou para realizar grandes coisas. Assim, aprendemos a servir a Deus fielmente, mesmo em situações difíceis. O blog Fé e Reflexões resume bem: “a verdadeira fé se revela não quando entendemos tudo, mas quando obedecemos e confiamos que Deus tem um plano perfeito para nossas vidas”. Somos chamados a confiar em Deus e fazer o que Ele pede, sabendo que Ele guia cada passo, mesmo quando não vemos a rota completa.
-
Esperança na redenção: Desde o princípio, Gênesis afirma que Deus já tinha um plano de salvação. O “protoevangelho” de Gn 3:15 é um lembrete de que Deus promete reverter o mal em bem. Como salienta a Escritura, mesmo após a queda “Deus não os destruiu, mas revelou Seu pacto da graça… prometendo um Salvador (Gn 3:15)”. Para o cristão de hoje, isso dá esperança firme: sabemos que Deus já venceu o pecado e a morte por meio de Jesus Cristo. Não importa o tamanho do problema ou do pecado, Deus é soberano e fiel para cumprir suas promessas. As histórias de Gênesis nos ensinam que Deus continua trabalhando para restaurar o que foi perdido. José entendeu isso ao dizer aos irmãos: “vocês intentaram o mal contra mim, mas Deus o tornou em bem” (Gn 50:20). Em nossa vida diária, podemos seguir em frente com a confiança de que o Senhor está conosco, transformando dificuldades em bênçãos e conduzindo-nos a um futuro de redenção.
Conclusão
O livro de Gênesis molda nossa visão de Deus como Criador soberano, fiel em suas promessas e Senhor da história. Essas páginas iniciais mostram que Deus é onipotente (ele criou tudo) e, ao mesmo tempo, misericordioso (prometeu um Redentor quando nós falhamos). Para nós hoje, essa mensagem é encorajadora: o mesmo Deus que falou com Adão, Noé e Abraão é o Deus que fala conosco e cumpre cada promessa. Assim, podemos viver com fé, sabendo que Cristo está no centro de tudo o que Gênesis anuncia. A história de Gênesis aponta para Jesus – e em Cristo “toda a criação será restaurada” (Rm 8:21) – dando-nos esperança e paz no caminho da vida. Confiemos no Senhor, pois Ele é fiel para realizar em nós o que prometeu desde o princípio.
Fontes: Esta reflexão reuniu ensinamentos bíblicos fundamentados na teologia reformada. As Escrituras de Gênesis e os comentários de autores reformados foram citados para apoiar cada ponto (por exemplo, Gn 3:15, Gn 15:6, Gn 22, e passagens de Paulo). As lições extraídas refletem tanto a simplicidade da narrativa quanto a profundidade do plano de salvação que vem de Deus.
-
-
 @ 3eba5ef4:751f23ae
2025-05-02 01:56:09
@ 3eba5ef4:751f23ae
2025-05-02 01:56:09Crypto Insights
secp256k1lab: An Insecure Python Library That Makes Bitcoin Safer
Some Bitcoin developers have long believed in the need for a unified, reusable cryptographic BIP reference standard for secp256k1. Blockstream Research has released secp256k1lab — an intentionally insecure new Python library designed for prototyping, experimentation, and BIP specifications.
This library is NOT intended for production use (it lacks constant-time protections and is thus vulnerable to side-channel attacks). However, it fills a gap by providing a clean and consistent reference implementation of secp256k1 functionality, including BIP-340 style Schnorr signatures, ECDH, and low-level field/group operations. Its goal: to make future BIP authoring simpler and more secure by avoiding redundant, one-off implementations. For BIP authors, this means less custom code, fewer specification bugs, and a clearer path from prototype to proposal.
Block-Based Time-Based One-Time Passwords for Secure Passphrase Validation in Bitcoin Wallets
This article introduces a method for passphrase validation and Bitcoin software wallet access control using a block-based time-based one-time password (TOTP) system.
Unlike traditional TOTP systems, this method uses blockchain data — specifically Bitcoin block height and block hash — combined with securely stored cryptographic secrets to generate a 6-digit dynamic verification code with the following security properties:
-
Two-Factor Protection: Combines device possession and blockchain-derived time-based data.
-
Replay Resistance: Codes change with every block (~10-min cycle).
-
Minimal Attack Surface: Passphrase never typed or copied.
-
Hardware-Backed Secrets: Mobile app secret stored in non-exportable secure hardware.
Bitcoin Feature Matrix: Tracking Interoperability of Bitcoin Products/Services
You can use this page on Bitcoin Opentech to track interoperability among Bitcoin products and services.
Tracking Bitcoin Soft Fork Proposals in One Place
bitcoin.softforks.org aggregates various Bitcoin soft fork proposals, including components, implementation primitives, use cases, and users.
Ethereum Community Explores Replacing EVM with RISC-V — Spotlight on CKB-VM Experience
Vitalik recently proposed the idea of replacing the EVM with RISC-V on the Ethereum forum, citing the design of CKB-VM as a reference. This has sparked active discussion in both communities around RISC-V as a technical direction. As the conversation deepens, the original design decisions behind CKB-VM have resurfaced, drawing renewed interest and encouraging more developers to study its architecture and lessons.
CKB is the Layer 1 blockchain of the Nervos Network. Its smart contract model, called the Cell model, is inspired by Bitcoin’s UTXO system. It uses the RISC-V–based CKB-VM to enable efficient and multi-language smart contract execution. Find more details in:
-
A Blockchain VM Built on RISC-V (The Birth of CKB-VM Part 1)
-
CKB-VM: Its Inspiration, Design, and Strengths (The Birth of CKB-VM, Part 2)
-
How to Have Fun with CKB-VM (The Birth of CKB-VM, Part 3)
Integrating Taproot Assets into Ark
Ark Labs shared their proof-of-concept of integrating Taproot Assets into the off-chain batching layer of Ark. They introduced tVTXOs (tokenized Virtual Transaction Outputs) — virtual outputs that embed Taproot Asset commitments.
tVTXOs behave like regular VTXOs, spendable off-chain and pre-signable for unilateral exits, but with two additional features:
-
Asset Commitments: Embedded in PkScript using Taproot’s internal key and TapTree structure.
-
Transfer Proof Files: A cryptographically linked, deterministic chain of off-chain proofs tracking asset inclusion. These can be activated via on-chain metadata to exit the Taproot Asset ecosystem.
Erk: An Ark Protocol Upgrade Removing User Round Interactions
Erk is a novel variant of the Ark protocol that introduces refund transactions with rebindable signatures. This allows users to pre-sign outputs that the server can safely refresh without needing the user to be online for each round — addressing one of Ark’s limitations.
Another feature of Erk is “perpetual offline refresh” — users can bulk pre-sign future refreshes. With watchtowers monitoring the protocol, users can stay offline indefinitely while their funds remain safe.
Robosats: No-KYC Lightning P2P Trading
RoboSats is an open-source, no-KYC Lightning P2P exchange using LN Hodl invoices to minimize custodial requirements and trust. Operated via the Tor browser, it offers a simple and low-fee user experience.
Find more in their GitHub repo and user guide.
Advancements in Lightning Infrastructure
OpenSats highlights several key Lightning infrastructure advancements:
-
Lightning Splicing: Allows dynamic channel capacity adjustment without downtime, simplifying liquidity management and reducing costs.
-
Validating Lightning Signer (VLS): Shifts key storage and transaction validation to an external signer. Even if a node is compromised, the attacker can’t access or misuse private keys.
-
BLAST (Big Lightning Automated Simulation Tool): Designed to provide a stable modeling and simulation framework of the Lightning Network for developers and node operators.
-
Lampo: A modular, community-driven development toolkit and node implementation built on Lightning Dev Kit (LDK).
-
Lnprototest: A Python-based testing library to help developers validate protocol adherence across different implementations.
Citrea Launches Clementine: A BitVM-Based Trust-Minimized 2-Way Peg Bridge
Rollup Citrea has deployed Clementine Bridge on Bitcoin testnet — the first fully BitVM-based bridge design on Bitcoin testnet. Clementine is Citrea’s trust-minimized, two-way peg solution powered by:
-
Bitcoin and Citrea’s light client proofs
-
Zero-knowledge proof verifier in BitVM
As long as one single verifier in the BitVM setup is honest, Clementine remains secure — a major improvement over existing approaches (e.g., open and closed federations). Paired with Citrea’s trustless light client, Clementine minimizes trust in Citrea’s bridge design and doesn’t require a soft fork.
Find more details in Clementine Whitepaper and Feature Overview.
Five Reasons RISC-V Is the Best Architecture for the BitVMX Proving System
Fairgate Labs, the main developers behind BitVMX, outlined five key reasons why RISC-V is the optimal choice for BitVMX:
-
Open and Universal: RISC-V as a standard with no IP barriers
-
Mature Tooling: A rich ecosystem of compilers and debuggers
-
Opcode Simplicity
-
High-Level Language Support
-
Universal Verification
Top Reads on Blockchain and Beyond
Demand Outpaces Licensing: LuckyMiner Drives Home Mining Boom Amid Controversy
LuckyMiner, a Bitcoin mining startup based in Shenzhen, China, is gaining traction with its mini miners. Their products are clones of the open-source Bitaxe miners from the U.S. However, Bitaxe is licensed under CERN-OHL-S-2.0, which requires all modifications to be open-sourced—something LuckyMiner has not complied with.
According to this post, LuckyMiner's founder openly admitted to violating the license and claimed that while their LuckyMiner devices for retail customers don’t comply with the open-source terms, they also produce fully license-compliant Bitaxes for business clients, while simultaneously cloning mining equipment from Braiins.
Against Burning Quantum-Vulnerable Bitcoins
Jameson Lopp has previously argued in favor of burning bitcoin in vulnerable addresses, to prevent funds from being taken by those who win the quantum computing race.
Guillaume Girard from UTXO Management disagrees, offering these counterpoints:
-
Property rights violation: Burning coins without the owner’s consent undermines the very principle of property rights. Forcing coins into unspendability erodes the core Bitcoin ethos of ownership and control.
-
Ethical concerns: While burning these coins may prevent quantum theft, it also punishes users who lost wallets or don’t understand the quantum threat—offering no chance for recovery.
Instead of burning, he proposes more constructive steps:
- Hourglass: Mitigates the downsides of both “confiscatory” and “liquidation” approaches – by limiting the potential supply shock of a quantum event, without burning coins or flooding markets.
This solution, proposed by Hunter Beast, aims to be the “least damaging” option and is currently under review by developers. Additionally, Hunter Beast has already proposed BIP 360 to bring Post-Quantum Cryptography (PQC) to Bitcoin with a new address type.
Old Miners, New Heat: Mining-as-Heating Might Just Work
BitMEX reviewed the Heatbit Trio—a Bitcoin miner repurposed into a room heater redesigned with a quiet fan.
The reviewer found the Heatbit concept commercially appealing and believes the heating-mining hybrid space is worth watching. The rate of improvement in ASIC efficiencies will decline (partly due to the limits of Moore’s Law), such that ASICs can economically mine Bitcoin for much longer—possibly up to 10 years. With fewer new technical risks, production costs should also drop. When that happens, integrating mining with heating systems may become practical.
Open, Instant, Borderless Payments: Stablecoins and Their Future
This a16z report explores how stablecoins are poised to change the global payments landscape—and who stands to benefit most.
The report sees stablecoins the "WhatsApp moment for money," enabling international transfers nearly free and instant. It also stresses that only two types of stablecoins are considered trustworthy: fiat-backed or asset-backed. The so-called Strategy-Backed Synthetic Dollars (SBSDs) are NOT considered to be a reliable store of value or medium of exchange.
-
-
 @ 6fc114c7:8f4b1405
2025-05-01 23:57:44
@ 6fc114c7:8f4b1405
2025-05-01 23:57:44Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s a forgotten password, a damaged seed backup, or simply one wrong transfer, the stress can be overwhelming. But there’s a silver lining — Crypt Recver is here to help! With our expert-led recovery services, you can reclaim your lost Bitcoin and other cryptos safely and swiftly.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in resolving some of the most complex wallet-related issues. Our team of skilled engineers has the tools and expertise to tackle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is critical in crypto recovery. Our optimized systems ensure that you can regain access to your funds quickly, aiming for speed without sacrificing security. With a 90%+ success rate, you can trust us to fight against the clock on your behalf.
🔒 Privacy is Our Priority Your confidentiality matters. Every recovery session is handled with the utmost care, ensuring all processes are encrypted and confidential. You can rest easy, knowing your sensitive information stays private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques allow for maximum efficiency in recovery. No matter how challenging your case may be, our technology is designed to give you the best chance at getting your crypto back.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us handle the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure, new wallet. Private Key Generation: Lost your private key? Don’t worry. Our experts can help you regain control using advanced methods — all while ensuring your privacy remains intact. ⚠️ What We Don’t Do While we can handle many scenarios, there are some limitations. For example, we cannot recover funds stored in custodial wallets, or cases where there is a complete loss of four or more seed words without any partial info available. We’re transparent about what’s possible, so you know what to expect.
Don’t Let Lost Crypto Hold You Back! ⏳ Did you know that 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate through it all.
🛡️ Real-Time Dust Attack Protection Protecting your privacy goes beyond just recovery. Our services include dust attack protection, which keeps your activity anonymous and your funds secure. Our suite will shield your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Are you ready to reclaim your lost crypto? Don’t wait until it’s too late!
👉 Request Wallet Recovery Help Now!
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on:
✉️ Telegram: Chat with Us on Telegram 💬 WhatsApp: Message Us on WhatsApp Crypt Recver is your trusted partner in the world of cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with Crypt Recver!Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s a forgotten password, a damaged seed backup, or simply one wrong transfer, the stress can be overwhelming. But there’s a silver lining — Crypt Recver is here to help! With our expert-led recovery services, you can reclaim your lost Bitcoin and other cryptos safely and swiftly.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions
At Crypt Recver, we specialize in resolving some of the most complex wallet-related issues. Our team of skilled engineers has the tools and expertise to tackle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery
We understand that time is critical in crypto recovery. Our optimized systems ensure that you can regain access to your funds quickly, aiming for speed without sacrificing security. With a 90%+ success rate, you can trust us to fight against the clock on your behalf.
🔒 Privacy is Our Priority
Your confidentiality matters. Every recovery session is handled with the utmost care, ensuring all processes are encrypted and confidential. You can rest easy, knowing your sensitive information stays private.
💻 Advanced Technology
Our proprietary tools and brute-force optimization techniques allow for maximum efficiency in recovery. No matter how challenging your case may be, our technology is designed to give you the best chance at getting your crypto back.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us handle the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure, new wallet.
- Private Key Generation: Lost your private key? Don’t worry. Our experts can help you regain control using advanced methods — all while ensuring your privacy remains intact.
⚠️ What We Don’t Do
While we can handle many scenarios, there are some limitations. For example, we cannot recover funds stored in custodial wallets, or cases where there is a complete loss of four or more seed words without any partial info available. We’re transparent about what’s possible, so you know what to expect.
 # Don’t Let Lost Crypto Hold You Back! ⏳
# Don’t Let Lost Crypto Hold You Back! ⏳Did you know that 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate through it all.
🛡️ Real-Time Dust Attack Protection
Protecting your privacy goes beyond just recovery. Our services include dust attack protection, which keeps your activity anonymous and your funds secure. Our suite will shield your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!
Are you ready to reclaim your lost crypto? Don’t wait until it’s too late!
👉 Request Wallet Recovery Help Now!
📞 Need Immediate Assistance? Connect with Us!
For real-time support or questions, reach out to our dedicated team on:
- ✉️ Telegram: Chat with Us on Telegram
- 💬 WhatsApp: Message Us on WhatsApp
Crypt Recver is your trusted partner in the world of cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with Crypt Recver!
-
 @ 000002de:c05780a7
2025-05-01 23:17:11
@ 000002de:c05780a7
2025-05-01 23:17:11A lot of typing has been done comparing various right wing figures and people like Donald Trump and Elon Mush to Fascism and Nazism. It is frankly pretty absurd at this point. I'd be with them if they were just talking about these people being authoritarians. They clearly are in many ways. I'm not a fan.
But very little is said in a "non-partisan" way about the left. This is gonna be short and is meant to peak your curiosity to go and do some research for yourself.
The economist Milton Friedman famously said.
"After the fall of communism, everybody in the world agreed that socialism was a failure. Everybody in the world, more or less, agreed that capitalism was a success. And every capitalist country in the world apparently deduced from that what the West needed was more socialism."
This was said a long time ago and it is still the case. People espouse socialist ideas without even a concern about being called out for it. The same is NOT true of fascism or even traditional American patriotism.
But many of you may not realize just how deep the rot of socialism goes. Most people agree that the USSR committed terrible acts and was a failure. Before the creation of the USSR two socialists movements fought for power and control, the Bolsheviks and Mensheviks. The primary difference between the two groups was how to bring about socialism. The Bolsheviks led by Lenin favored a more radical revolutionary force led by a small group. The Mensheviks, led by Julius Martov, preferred a larger, more democratic rise to power. They supported a more gradual rise of socialism. In October of 1917 the Bolsheviks seized power in Russia in a bloody revolution.
Even to this day there are two different minds around how to bring about socialism. In the US the Menshevik approach is the one more popular. People like Bernie and AOC are this type of socialist. But make no mistake. They want to bring about a socialist utopian society. The type of system we have seen fail time and time again.
A few years ago I heard about another socialist movement and was frankly shocked that I had never heard about it before. In 1890 Britain a group of socialists formed an organization called the Fabian Society. The Fabians were/are socialists. But they believe in gradual incrementalism to bring about socialism. So what did the do you ask? They were at the center of the founding of the Labour party in the UK. Now, you might say. Big deal. But here's the weird thing. The Fabian Society's coat of arms was literally a wolf in sheep's clothing
They sought to bring about socialism covertly through democratic processes by presenting themselves as more moderate politicians. They have worked for decades to bring about socialism in the UK. If you don't count Margret Thatcher's era they've done a pretty great job. The UK is a mess.
So what does this have to do with May Day or Labor day for that matter? Well, socialists are at the center of every labor movement and celebrations like May day. Socialist ideas have been pumped into the government textbooks in the US for decades. Teachers are instructed in Universities full of believers in this wolf in sheep's clothing movement of democratic socialism.
Socialism leads to death and poverty. I'm not here to say that the US economy is the example for what the world should do. I'm a free market guy. We live in a corporatism led economy where the state partners with corporations to screw many in the US as well as the world. But I can tell you this. Socialism would be even worse.
The famous and infamous Russian anarchist Emma Goldman upon returning from her visit to the USSR was broken hearted. She had been a supporter of the revolution, but when she saw it with her own eyes she had a change of heart.
The compassion that seems to be a part of socialism is a lie. You can't institutionalize compassion. It has to come from the people, not a system. We should care for our brothers and sisters. But WE have to do it. We can't take from one group and give to another. We can't surrender our liberties to those that say they will take care of it for us. We have to do it. Capitalism is amoral. The free market is amoral. Both require us to be moral and show the way.
I hope this sparks your interest into looking into the history around socialist movements across the globe. I don't doubt that some have good motives, but the results are disastrous for the masses.
originally posted at https://stacker.news/items/968901
-
 @ d34e832d:383f78d0
2025-04-26 15:04:51
@ d34e832d:383f78d0
2025-04-26 15:04:51Raspberry Pi-based voice assistant
This Idea details the design and deployment of a Raspberry Pi-based voice assistant powered by the Google Gemini AI API. The system combines open hardware with modern AI services to create a low-cost, flexible, and educational voice assistant platform. By leveraging a Raspberry Pi, basic audio hardware, and Python-based software, developers can create a functional, customizable assistant suitable for home automation, research, or personal productivity enhancement.
1. Voice assistants
Voice assistants have become increasingly ubiquitous, but commercially available systems like Alexa, Siri, or Google Assistant come with significant privacy and customization limitations.
This project offers an open, local, and customizable alternative, demonstrating how to build a voice assistant using Google Gemini (or OpenAI’s ChatGPT) APIs for natural language understanding.Target Audience:
- DIY enthusiasts - Raspberry Pi hobbyists - AI developers - Privacy-conscious users
2. System Architecture
2.1 Hardware Components
| Component | Purpose | |:--------------------------|:----------------------------------------| | Raspberry Pi (any recent model, 4B recommended) | Core processing unit | | Micro SD Card (32GB+) | Operating System and storage | | USB Microphone | Capturing user voice input | | Audio Amplifier + Speaker | Outputting synthesized responses | | 5V DC Power Supplies (2x) | Separate power for Pi and amplifier | | LEDs + Resistors (optional)| Visual feedback (e.g., recording or listening states) |
2.2 Software Stack
| Software | Function | |:---------------------------|:----------------------------------------| | Raspberry Pi OS (Lite or Full) | Base operating system | | Python 3.9+ | Programming language | | SpeechRecognition | Captures and transcribes user voice | | Google Text-to-Speech (gTTS) | Converts responses into spoken audio | | Google Gemini API (or OpenAI API) | Powers the AI assistant brain | | Pygame | Audio playback for responses | | WinSCP + Windows Terminal | File transfer and remote management |
3. Hardware Setup
3.1 Basic Connections
- Microphone: Connect via USB port.
- Speaker and Amplifier: Wire from Raspberry Pi audio jack or via USB sound card if better quality is needed.
- LEDs (Optional): Connect through GPIO pins, using 220–330Ω resistors to limit current.
3.2 Breadboard Layout (Optional for LEDs)
| GPIO Pin | LED Color | Purpose | |:---------|:-----------|:--------------------| | GPIO 17 | Red | Recording active | | GPIO 27 | Green | Response playing |
Tip: Use a small breadboard for quick prototyping before moving to a custom PCB if desired.
4. Software Setup
4.1 Raspberry Pi OS Installation
- Use Raspberry Pi Imager to flash Raspberry Pi OS onto the Micro SD card.
- Initial system update:
bash sudo apt update && sudo apt upgrade -y
4.2 Python Environment
-
Install Python virtual environment:
bash sudo apt install python3-venv python3 -m venv voice-env source voice-env/bin/activate -
Install required Python packages:
bash pip install SpeechRecognition google-generativeai pygame gtts
(Replace
google-generativeaiwithopenaiif using OpenAI's ChatGPT.)4.3 API Key Setup
- Obtain a Google Gemini API key (or OpenAI API key).
- Store safely in a
.envfile or configure as environment variables for security:bash export GEMINI_API_KEY="your_api_key_here"
4.4 File Transfer
- Use WinSCP or
scpcommands to transfer Python scripts to the Pi.
4.5 Example Python Script (Simplified)
```python import speech_recognition as sr import google.generativeai as genai from gtts import gTTS import pygame import os
genai.configure(api_key=os.getenv('GEMINI_API_KEY')) recognizer = sr.Recognizer() mic = sr.Microphone()
pygame.init()
while True: with mic as source: print("Listening...") audio = recognizer.listen(source)
try: text = recognizer.recognize_google(audio) print(f"You said: {text}") response = genai.generate_content(text) tts = gTTS(text=response.text, lang='en') tts.save("response.mp3") pygame.mixer.music.load("response.mp3") pygame.mixer.music.play() while pygame.mixer.music.get_busy(): continue except Exception as e: print(f"Error: {e}")```
5. Testing and Execution
- Activate the Python virtual environment:
bash source voice-env/bin/activate - Run your main assistant script:
bash python3 assistant.py - Speak into the microphone and listen for the AI-generated spoken response.
6. Troubleshooting
| Problem | Possible Fix | |:--------|:-------------| | Microphone not detected | Check
arecord -l| | Audio output issues | Checkaplay -l, use a USB DAC if needed | | Permission denied errors | Verify group permissions (audio, gpio) | | API Key Errors | Check environment variable and internet access |
7. Performance Notes
- Latency: Highly dependent on network speed and API response time.
- Audio Quality: Can be enhanced with a better USB microphone and powered speakers.
- Privacy: Minimal data retention if using your own Gemini or OpenAI account.
8. Potential Extensions
- Add hotword detection ("Hey Gemini") using Snowboy or Porcupine libraries.
- Build a local fallback model to answer basic questions offline.
- Integrate with home automation via MQTT, Home Assistant, or Node-RED.
- Enable LED animations to visually indicate listening and responding states.
- Deploy with a small eInk or OLED screen for text display of answers.
9. Consider
Building a Gemini-powered voice assistant on the Raspberry Pi empowers individuals to create customizable, private, and cost-effective alternatives to commercial voice assistants. By utilizing accessible hardware, modern open-source libraries, and powerful AI APIs, this project blends education, experimentation, and privacy-centric design into a single hands-on platform.
This guide can be adapted for personal use, educational programs, or even as a starting point for more advanced AI-based embedded systems.
References
- Raspberry Pi Foundation: https://www.raspberrypi.org
- Google Generative AI Documentation: https://ai.google.dev
- OpenAI Documentation: https://platform.openai.com
- SpeechRecognition Library: https://pypi.org/project/SpeechRecognition/
- gTTS Documentation: https://pypi.org/project/gTTS/
- Pygame Documentation: https://www.pygame.org/docs/
-
 @ 2183e947:f497b975
2025-05-01 22:33:48
@ 2183e947:f497b975
2025-05-01 22:33:48Most darknet markets (DNMs) are designed poorly in the following ways:
1. Hosting
Most DNMs use a model whereby merchants fill out a form to create their listings, and the data they submit then gets hosted on the DNM's servers. In scenarios where a "legal" website would be forced to censor that content (e.g. a DMCA takedown order), DNMs, of course, do not obey. This can lead to authorities trying to find the DNM's servers to take enforcement actions against them. This design creates a single point of failure.
A better design is to outsource hosting to third parties. Let merchants host their listings on nostr relays, not on the DNM's server. The DNM should only be designed as an open source interface for exploring listings hosted elsewhere, that way takedown orders end up with the people who actually host the listings, i.e. with nostr relays, and not with the DNM itself. And if a nostr relay DOES go down due to enforcement action, it does not significantly affect the DNM -- they'll just stop querying for listings from that relay in their next software update, because that relay doesn't work anymore, and only query for listings from relays that still work.
2. Moderation
Most DNMs have employees who curate the listings on the DNM. For example, they approve/deny listings depending on whether they fit the content policies of the website. Some DNMs are only for drugs, others are only for firearms. The problem is, to approve a criminal listing is, in the eyes of law enforcement, an act of conspiracy. Consequently, they don't just go after the merchant who made the listing but the moderators who approved it, and since the moderators typically act under the direction of the DNM, this means the police go after the DNM itself.
A better design is to outsource moderation to third parties. Let anyone call themselves a moderator and create lists of approved goods and services. Merchants can pay the most popular third party moderators to add their products to their lists. The DNM itself just lets its users pick which moderators to use, such that the user's choice -- and not a choice by the DNM -- determines what goods and services the user sees in the interface.
That way, the police go after the moderators and merchants rather than the DNM itself, which is basically just a web browser: it doesn't host anything or approve of any content, it just shows what its users tell it to show. And if a popular moderator gets arrested, his list will still work for a while, but will gradually get more and more outdated, leading someone else to eventually become the new most popular moderator, and a natural transition can occur.
3. Escrow
Most DNMs offer an escrow solution whereby users do not pay merchants directly. Rather, during the Checkout process, they put their money in escrow, and request the DNM to release it to the merchant when the product arrives, otherwise they initiate a dispute. Most DNMs consider escrow necessary because DNM users and merchants do not trust one another; users don't want to pay for a product first and then discover that the merchant never ships it, and merchants don't want to ship a product first and then discover that the user never pays for it.
The problem is, running an escrow solution for criminals is almost certain to get you accused of conspiracy, money laundering, and unlicensed money transmission, so the police are likely to shut down any DNM that does this. A better design is to oursource escrow to third parties. Let anyone call themselves an escrow, and let moderators approve escrows just like they approve listings. A merchant or user who doesn't trust the escrows chosen by a given moderator can just pick a different moderator. That way, the police go after the third party escrows rather than the DNM itself, which never touches user funds.
4. Consequences
Designing a DNM along these principles has an interesting consequence: the DNM is no longer anything but an interface, a glorified web browser. It doesn't host any content, approve any listings, or touch any money. It doesn't even really need a server -- it can just be an HTML file that users open up on their computer or smart phone. For two reasons, such a program is hard to take down:
First, it is hard for the police to justify going after the DNM, since there are no charges to bring. Its maintainers aren't doing anything illegal, no more than Firefox does anything illegal by maintaining a web browser that some people use to browse illegal content. What the user displays in the app is up to them, not to the code maintainers. Second, if the police decided to go after the DNM anyway, they still couldn't take it down because it's just an HTML file -- the maintainers do not even need to run a server to host the file, because users can share it with one another, eliminating all single points of failure.
Another consequence of this design is this: most of the listings will probably be legal, because there is more demand for legal goods and services than illegal ones. Users who want to find illegal goods would pick moderators who only approve those listings, but everyone else would use "legal" moderators, and the app would not, at first glance, look much like a DNM, just a marketplace for legal goods and services. To find the illegal stuff that lurks among the abundant legal stuff, you'd probably have to filter for it via your selection of moderators, making it seem like the "default" mode is legal.
5. Conclusion
I think this DNM model is far better than the designs that prevail today. It is easier to maintain, harder to take down, and pushes the "hard parts" to the edges, so that the DNM is not significantly affected even if a major merchant, moderator, or escrow gets arrested. I hope it comes to fruition.
-
 @ 34f1ddab:2ca0cf7c
2025-05-01 22:14:34
@ 34f1ddab:2ca0cf7c
2025-05-01 22:14:34In the world of cryptocurrency, the stakes are high, and losing access to your digital assets can be a nightmare. But fear not — Crypt Recver is here to turn that nightmare into a dream come true! With expert-led recovery services and cutting-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
Why Choose Crypt Recver? 🤔 🔑 Expertise You Can Trust At Crypt Recver, we combine state-of-the-art technology with skilled engineers who have a proven track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or dealt with damaged hardware wallets, our team is equipped to help.
⚡ Fast Recovery Process Time is of the essence when it comes to recovering lost funds. Crypt Recver’s systems are optimized for speed, enabling quick recoveries — so you can get back to what matters most: trading and investing.
🎯 High Success Rate With over a 90% success rate, our recovery team has helped countless clients regain access to their lost assets. We understand the intricacies of cryptocurrency and are dedicated to providing effective solutions.
🛡️ Confidential & Secure Your privacy is our priority. All recovery sessions at Crypt Recver are encrypted and kept entirely confidential. You can trust us with your information, knowing that we maintain the highest standards of security.
🔧 Advanced Recovery Tools We use proprietary tools and techniques to handle complex recovery scenarios, from recovering corrupted wallets to restoring coins from invalid addresses. No matter how challenging the situation, we have a plan.
Our Recovery Services Include: 📈 Bitcoin Recovery: Have you lost access to your Bitcoin wallet? We can help you recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds! Cold Wallet Restoration: Did your cold wallet fail? We specialize in extracting assets safely and securely. Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security. Don’t Let Lost Crypto Ruin Your Day! 🕒 With an estimated 3 to 3.4 million BTC lost forever, it’s critical to act swiftly when facing access issues. Whether you’ve been a victim of a dust attack or have simply forgotten your key, Crypt Recver offers the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now! Ready to get your cryptocurrency back? Don’t let uncertainty hold you back!
👉 Request Wallet Recovery Help Today!
Need Immediate Assistance? 📞 For quick queries or support, connect with us on:
✉️ Telegram: Chat with Us on Telegram 💬 WhatsApp: Message Us on WhatsApp Trust Crypt Recver for the Best Crypto Recovery Service — Get back to trading with confidence! 💪In the world of cryptocurrency, the stakes are high, and losing access to your digital assets can be a nightmare. But fear not — Crypt Recver is here to turn that nightmare into a dream come true! With expert-led recovery services and cutting-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
 # Why Choose Crypt Recver? 🤔
# Why Choose Crypt Recver? 🤔🔑 Expertise You Can Trust
At Crypt Recver, we combine state-of-the-art technology with skilled engineers who have a proven track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or dealt with damaged hardware wallets, our team is equipped to help.
⚡ Fast Recovery Process
Time is of the essence when it comes to recovering lost funds. Crypt Recver’s systems are optimized for speed, enabling quick recoveries — so you can get back to what matters most: trading and investing.
🎯 High Success Rate
With over a 90% success rate, our recovery team has helped countless clients regain access to their lost assets. We understand the intricacies of cryptocurrency and are dedicated to providing effective solutions.
🛡️ Confidential & Secure
Your privacy is our priority. All recovery sessions at Crypt Recver are encrypted and kept entirely confidential. You can trust us with your information, knowing that we maintain the highest standards of security.
🔧 Advanced Recovery Tools
We use proprietary tools and techniques to handle complex recovery scenarios, from recovering corrupted wallets to restoring coins from invalid addresses. No matter how challenging the situation, we have a plan.
 # Our Recovery Services Include: 📈
# Our Recovery Services Include: 📈- Bitcoin Recovery: Have you lost access to your Bitcoin wallet? We can help you recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds!
- Cold Wallet Restoration: Did your cold wallet fail? We specialize in extracting assets safely and securely.
- Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security.
Don’t Let Lost Crypto Ruin Your Day! 🕒
With an estimated 3 to 3.4 million BTC lost forever, it’s critical to act swiftly when facing access issues. Whether you’ve been a victim of a dust attack or have simply forgotten your key, Crypt Recver offers the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now!
Ready to get your cryptocurrency back? Don’t let uncertainty hold you back!
👉 Request Wallet Recovery Help Today!
Need Immediate Assistance? 📞
For quick queries or support, connect with us on:
- ✉️ Telegram: Chat with Us on Telegram
- 💬 WhatsApp: Message Us on WhatsApp
Trust Crypt Recver for the Best Crypto Recovery Service — Get back to trading with confidence! 💪
-
 @ d34e832d:383f78d0
2025-04-26 14:33:06
@ d34e832d:383f78d0
2025-04-26 14:33:06Gist
This Idea presents a blueprint for creating a portable, offline-first education server focused on Free and Open Source Software (FOSS) topics like Bitcoin fundamentals, Linux administration, GPG encryption, and digital self-sovereignty. Using the compact and powerful Nookbox G9 NAS unit, we demonstrate how to deliver accessible, decentralized educational content in remote or network-restricted environments.
1. Bitcoin, Linux, and Cryptographic tools
Access to self-sovereign technologies such as Bitcoin, Linux, and cryptographic tools is critical for empowering individuals and communities. However, many areas face internet connectivity issues or political restrictions limiting access to online resources.
By combining a high-performance mini NAS server with a curated library of FOSS educational materials, we can create a mobile "university" that delivers critical knowledge independently of centralized networks.
2. Hardware Platform: Nookbox G9 Overview
The Nookbox G9 offers an ideal balance of performance, portability, and affordability for this project.
2.1 Core Specifications
| Feature | Specification | |:------------------------|:---------------------------------------| | Form Factor | 1U Rackmount mini-NAS | | Storage | Up to 8TB (4×2TB M.2 NVMe SSDs) | | M.2 Interface | PCIe Gen 3x2 per drive slot | | Networking | Dual 2.5 Gigabit Ethernet ports | | Power Consumption | 11–30 Watts (typical usage) | | Default OS | Windows 11 (to be replaced with Linux) | | Linux Compatibility | Fully compatible with Ubuntu 24.10 |
3. FOSS Education Server Design
3.1 Operating System Setup
- Replace Windows 11 with a clean install of Ubuntu Server 24.10.
- Harden the OS:
- Enable full-disk encryption.
- Configure UFW firewall.
- Disable unnecessary services.
3.2 Core Services Deployed
| Service | Purpose | |:--------------------|:-----------------------------------------| | Nginx Web Server | Host offline courses and documentation | | Nextcloud (optional) | Offer private file sharing for students | | Moodle LMS (optional) | Deliver structured courses and quizzes | | Tor Hidden Service | Optional for anonymous access locally | | rsync/Syncthing | Distribute updates peer-to-peer |
3.3 Content Hosted
- Bitcoin: Bitcoin Whitepaper, Bitcoin Core documentation, Electrum Wallet tutorials.
- Linux: Introduction to Linux (LPIC-1 materials), bash scripting guides, system administration manuals.
- Cryptography: GPG tutorials, SSL/TLS basics, secure communications handbooks.
- Offline Tools: Full mirrors of sites like LearnLinux.tv, Bitcoin.org, and selected content from FSF.
All resources are curated to be license-compliant and redistributable in an offline format.
4. Network Configuration
- LAN-only Access: No reliance on external Internet.
- DHCP server setup for automatic IP allocation.
- Optional Wi-Fi access point using USB Wi-Fi dongle and
hostapd. - Access Portal: Homepage automatically redirects users to educational content upon connection.
5. Advantages of This Setup
| Feature | Advantage | |:-----------------------|:----------------------------------------| | Offline Capability | Operates without internet connectivity | | Portable Form Factor | Fits into field deployments easily | | Secure and Hardened | Encrypted, compartmentalized, and locked down | | Modular Content | Easy to update or expand educational resources | | Energy Efficient | Low power draw enables solar or battery operation | | Open Source Stack | End-to-end FOSS ecosystem, no vendor lock-in |
6. Deployment Scenarios
- Rural Schools: Provide Linux training without requiring internet.
- Disaster Recovery Zones: Deliver essential technical education in post-disaster areas.
- Bitcoin Meetups: Offer Bitcoin literacy and cryptography workshops in remote communities.
- Privacy Advocacy Groups: Teach operational security practices without risking network surveillance.
7. Performance Considerations
Despite PCIe Gen 3x2 limitations, the available bandwidth (~2GB/s theoretical) vastly exceeds the server's 2.5 Gbps network output (~250MB/s), making it more than sufficient for a read-heavy educational workload.
Thermal Management:
Given the G9’s known cooling issues, install additional thermal pads or heatsinks on the NVMe drives. Consider external USB-powered cooling fans for sustained heavy usage.
8. Ways To Extend
- Multi-language Support: Add localized course materials.
- Bitcoin Node Integration: Host a lightweight Bitcoin node (e.g., Bitcoin Core with pruning enabled or a complete full node) for educational purposes.
- Mesh Networking: Use Mesh Wi-Fi protocols (e.g., cjdns or Yggdrasil) to allow peer-to-peer server sharing without centralized Wi-Fi.
9. Consider
Building a Portable FOSS Education Server on a Nookbox G9 is a practical, scalable solution for democratizing technical knowledge, empowering communities, and defending digital sovereignty in restricted environments.
Through thoughtful system design—leveraging open-source software and secure deployment practices—we enable resilient, censorship-resistant education wherever it's needed.
📎 References
-
 @ 2cb30c36:cc7ecec1
2025-05-01 21:52:50
@ 2cb30c36:cc7ecec1
2025-05-01 21:52:50Test
This is a test
-
 @ 63616fef:5e05fd6a
2025-05-01 21:26:58
@ 63616fef:5e05fd6a
2025-05-01 21:26:58How to achieve net zero:
1) Vastly reduce reliable electric generation 2) Optimize for unreliable, and intermittent power generation
Long form article posted via untype.app
-
 @ 088436cd:9d2646cc
2025-05-01 21:01:55
@ 088436cd:9d2646cc
2025-05-01 21:01:55The arrival of the coronavirus brought not only illness and death but also fear and panic. In such an environment of uncertainty, people have naturally stocked up on necessities, not knowing when things will return to normal.
Retail shelves have been cleared out, and even online suppliers like Amazon and Walmart are out of stock for some items. Independent sellers on these e-commerce platforms have had to fill the gap. With the huge increase in demand, they have found that their inventory has skyrocketed in value.
Many in need of these items (e.g. toilet paper, hand sanitizer and masks) balk at the new prices. They feel they are being taken advantage of in a time of need and call for intervention by the government to lower prices. The government has heeded that call, labeling the independent sellers as "price gougers" and threatening sanctions if they don't lower their prices. Amazon has suspended seller accounts and law enforcement at all levels have threatened to prosecute. Prices have dropped as a result and at first glance this seems like a victory for fair play. But, we will have to dig deeper to understand the unseen consequences of this intervention.
We must look at the economics of the situation, how supply and demand result in a price and how that price acts as a signal that goes out to everyone, informing them of underlying conditions in the economy and helping coordinate their actions.
It all started with a rise in demand. Given a fixed supply (e.g., the limited stock on shelves and in warehouses), an increase in demand inevitably leads to higher prices. Most people are familiar with this phenomenon, such as paying more for airline tickets during holidays or surge pricing for rides.
Higher prices discourage less critical uses of scarce resources. For example, you might not pay $1,000 for a plane ticket to visit your aunt if you can get one for $100 the following week, but someone else might pay that price to visit a dying relative. They value that plane seat more than you.
*** During the crisis, demand surged and their shelves emptied even though
However, retail outlets have not raised prices. They have kept them low, so the low-value uses of things like toilet paper, masks and hand sanitizer has continued. Often, this "use" just takes the form of hoarding. At everyday low prices, it makes sense to buy hundreds of rolls and bottles. You know you will use them eventually, so why not stock up? And, with all those extra supplies in the closet and basement, you don't need to change your behavior much. You don't have to ration your use.
At the low prices, these scarce resources got bought up faster and faster until there was simply none left. The reality of the situation became painfully clear to those who didn't panic and got to the store late: You have no toilet paper and you're not going to any time soon.
However, if prices had been allowed to rise, a number of effects would have taken place that would have coordinated the behavior of everyone so that valuable resources would not have been wasted or hoarded, and everyone could have had access to what they needed.
On the demand side, if prices had been allowed to rise, people would have begun to self-ration. You might leave those extra plies on the roll next time if you know they will cost ten times as much to replace. Or, you might choose to clean up a spill with a rag rather than disposable tissue. Most importantly, you won't hoard as much. That 50th bottle of hand sanitizer might just not be worth it at the new, high price. You'll leave it on the shelf for someone else who may have none.
On the supply side, higher prices would have incentivized people to offer up more of their stockpiles for sale. If you have a pallet full of toilet paper in your basement and all of the sudden they are worth $15 per roll, you might just list a few online. But, if it is illegal to do so, you probably won't.
Imagine you run a business installing insulation and have a few thousand respirator masks on hand for your employees. During a pandemic, it is much more important that people breathe filtered air than that insulation get installed, and that fact is reflected in higher prices. You will sell your extra masks at the higher price rather than store them for future insulation jobs, and the scarce resource will be put to its most important use.
Producers of hand sanitizer would go into overdrive if prices were allowed to rise. They would pay their employees overtime, hire new ones, and pay a premium for their supplies, making sure their raw materials don't go to less important uses.
These kinds of coordinated actions all across the economy would be impossible without real prices to guide them. How do you know if it makes sense to spend an extra $10k bringing a thousand masks to market unless you know you can get more than $10 per mask? If the price is kept artificially low, you simply can't do it. The money just isn't there.
These are the immediate effects of a price change, but incredibly, price changes also coordinate people's actions across space and time.
Across space, there are different supply and demand conditions in different places, and thus prices are not uniform. We know some places are real "hot spots" for the virus, while others are mostly unaffected. High demand in the hot spots leads to higher prices there, which attracts more of the resource to those areas. Boxes and boxes of essential items would pour in where they are needed most from where they are needed least, but only if prices were allowed to adjust freely.
This would be accomplished by individuals and businesses buying low in the unaffected areas, selling high in the hot spots and subtracting their labor and transportation costs from the difference. Producers of new supply would know exactly where it is most needed and ship to the high-demand, high-price areas first. The effect of these actions is to increase prices in the low demand areas and reduce them in the high demand areas. People in the low demand areas will start to self-ration more, reflecting the reality of their neighbors, and people in the hotspots will get some relief.
However, by artificially suppressing prices in the hot spot, people there will simply buy up the available supply and run out, and it will be cost prohibitive to bring in new supply from low-demand areas.
Prices coordinate economic actions across time as well. Just as entrepreneurs and businesses can profit by transporting scarce necessities from low-demand to high-demand areas, they can also profit by buying in low-demand times and storing their merchandise for when it is needed most.
Just as allowing prices to freely adjust in one area relative to another will send all the right signals for the optimal use of a scarce resource, allowing prices to freely adjust over time will do the same.
When an entrepreneur buys up resources during low-demand times in anticipation of a crisis, she restricts supply ahead of the crisis, which leads to a price increase. She effectively bids up the price. The change in price affects consumers and producers in all the ways mentioned above. Consumers self-ration more, and producers bring more of the resource to market.
Our entrepreneur has done a truly incredible thing. She has predicted the future, and by so doing has caused every individual in the economy to prepare for a shortage they don't even know is coming! And, by discouraging consumption and encouraging production ahead of time, she blunts the impact the crisis will have. There will be more of the resource to go around when it is needed most.
On top of this, our entrepreneur still has her stockpile she saved back when everyone else was blithely using it up. She can now further mitigate the damage of the crisis by selling her stock during the worst of it, when people are most desperate for relief. She will know when this is because the price will tell her, but only if it is allowed to adjust freely. When the price is at its highest is when people need the resource the most, and those willing to pay will not waste it or hoard it. They will put it to its highest valued use.
The economy is like a big bus we are all riding in, going down a road with many twists and turns. Just as it is difficult to see into the future, it is difficult to see out the bus windows at the road ahead.
On the dashboard, we don't have a speedometer or fuel gauge. Instead we have all the prices for everything in the economy. Prices are what tell us the condition of the bus and the road. They tell us everything. Without them, we are blind.
Good times are a smooth road. Consumer prices and interest rates are low, investment returns are steady. We hit the gas and go fast. But, the road is not always straight and smooth. Sometimes there are sharp turns and rough patches. Successful entrepreneurs are the ones who can see what is coming better than everyone else. They are our navigators.
When they buy up scarce resources ahead of a crisis, they are hitting the brakes and slowing us down. When they divert resources from one area to another, they are steering us onto a smoother path. By their actions in the market, they adjust the prices on our dashboard to reflect the conditions of the road ahead, so we can prepare for, navigate and get through the inevitable difficulties we will face.
Interfering with the dashboard by imposing price floors or price caps doesn't change the conditions of the road (the number of toilet paper rolls in existence hasn't changed). All it does is distort our perception of those conditions. We think the road is still smooth--our heavy foot stomping the gas--as we crash onto a rocky dirt road at 80 miles per hour (empty shelves at the store for weeks on end).
Supply, demand and prices are laws of nature. All of this is just how things work. It isn't right or wrong in a moral sense. Price caps lead to waste, shortages and hoarding as surely as water flows downhill. The opposite--allowing prices to adjust freely--leads to conservation of scarce resources and their being put to their highest valued use. And yes, it leads to profits for the entrepreneurs who were able to correctly predict future conditions, and losses for those who weren't.
Is it fair that they should collect these profits? On the one hand, anyone could have stocked up on toilet paper, hand sanitizer and face masks at any time before the crisis, so we all had a fair chance to get the supplies cheaply. On the other hand, it just feels wrong that some should profit so much at a time when there is so much need.
Our instinct in the moment is to see the entrepreneur as a villain, greedy "price gouger". But we don't see the long chain of economic consequences the led to the situation we feel is unfair.
If it weren't for anti-price-gouging laws, the major retailers would have raised their prices long before the crisis became acute. When they saw demand outstrip supply, they would have raised prices, not by 100 fold, but gradually and long before anyone knew how serious things would have become. Late comers would have had to pay more, but at least there would be something left on the shelf.
As an entrepreneur, why take risks trying to anticipate the future if you can't reap the reward when you are right? Instead of letting instead of letting entrepreneurs--our navigators--guide us, we are punishing and vilifying them, trying to force prices to reflect a reality that simply doesn't exist.
In a crisis, more than any other time, prices must be allowed to fluctuate. To do otherwise is to blind ourselves at a time when danger and uncertainty abound. It is economic suicide.
In a crisis, there is great need, and the way to meet that need is not by pretending it's not there, by forcing prices to reflect a world where there isn't need. They way to meet the need is the same it has always been, through charity.
If the people in government want to help, the best way for the to do so is to be charitable and reduce their taxes and fees as much as possible, ideally to zero in a time of crisis. Amazon, for example, could instantly reduce the price of all crisis related necessities by 20% if they waived their fee. This would allow for more uses by more people of these scarce supplies as hoarders release their stockpiles on to the market, knowing they can get 20% more for their stock. Governments could reduce or eliminate their tax burden on high-demand, crisis-related items and all the factors that go into their production, with the same effect: a reduction in prices and expansion of supply. All of us, including the successful entrepreneurs and the wealthy for whom high prices are not a great burden, could donate to relief efforts.
These ideas are not new or untested. This is core micro economics. It has been taught for hundreds of years in universities the world over. The fact that every crisis that comes along stirs up ire against entrepreneurs indicates not that the economics is wrong, but that we have a strong visceral reaction against what we perceive to be unfairness. This is as it should be. Unfairness is wrong and the anger it stirs in us should compel us to right the wrong. Our anger itself isn't wrong, it's just misplaced.
Entrepreneurs didn't cause the prices to rise. Our reaction to a virus did that. We saw a serious threat and an uncertain future and followed our natural impulse to hoard. Because prices at major retail suppliers didn't rise, that impulse ran rampant and we cleared the shelves until there was nothing left. We ran the bus right off the road and them blamed the entrepreneurs for showing us the reality of our situation, for shaking us out of the fantasy of low prices.
All of this is not to say that entrepreneurs are high-minded public servants. They are just doing their job. Staking your money on an uncertain future is a risky business. There are big risks and big rewards. Most entrepreneurs just scrape by or lose their capital in failed ventures.
However, the ones that get it right must be allowed to keep their profits, or else no one will try and we'll all be driving blind. We need our navigators. It doesn't even matter if they know all the positive effects they are having on the rest of us and the economy as a whole. So long as they are buying low and selling high--so long as they are doing their job--they will be guiding the rest of us through the good times and the bad, down the open road and through the rough spots.
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 318ebaba:9a262eae
2025-05-01 20:28:44
@ 318ebaba:9a262eae
2025-05-01 20:28:44Heute soll es funktionieren
-
 @ 2ed3596e:98b4cc78
2025-05-01 20:27:18
@ 2ed3596e:98b4cc78
2025-05-01 20:27:18The Bitcoin Well Affiliate program is here! You can earn a bitcoin bonus of 21% of revenue generated from transactions every time someone you refer transacts on our platform. Bitcoin Well Affiliates can also complete bounty tasks to earn sats, such as Bitcoin Well video tutorials. The Affiliate program is our way of aligning incentives with our mission to enable independence.
How to apply for the Bitcoin Well Affiliate program
The Affiliate program is big folks in and bitcoin or folks with a LOT of experience with bitcoin and self-custody wallets; the most important quality is a passion for orange-pilling!
Bitcoin Well Affiliates earn more than double our referral commission (21% of revenue generated from transactions), get a custom Bitcoin Well Affiliate webpage to help you get referrals and unlock bounty tasks for bonus sats. You can apply to join the Affiliate program by clicking here.
How to earn your Bitcoin Well Referral bonus
To refer a customer to Bitcoin Well, have them sign up using your Bitcoin Well referral link, this can be found in your Bitcoin Well account under Rewards > Referrals. Your referred customers also get a sign up bonus of 1,000 Bitcoin Well. You get 500 points for each referral, too.
Your personal referral link will be https://bitcoinwell.com/app/ref/YOUR_WELLTAG. A person can also be referred by typing in your welltag in the Referral Code field on the sign up page.
The best part? Sats are AUTOMATICALLY paid to your designated Lightning Wallet.

Who is eligible to refer to Bitcoin Well?
The Bitcoin Well Affiliate program is available to anyone! However, our services are only available in Canada and the United States.
The Affiliate program includes referrals to business and High Net Worth Individuals that use our OTC desk.
How to hunt Affiliate bounty tasks and earn sats
Affiliates can hunt bounty tasks by making Bitcoin Well tutorials and uploading them to Youtube or X in exchange for sats.
Bounty tasks such as How to buy bitcoin (USA) on Bitcoin Well are a fantastic resource to generate referrals and boost traffic to your pages. Affiliate bounty tasks earn you 21,000-105,000 sats per video. \ \ Affiliate bounty tasks are only available to approved Bitcoin Well Affiliates. Read our Affiliate Bounty article for more details on submitting Affiliate bounties.
How does the Bitcoin Well referral program work?
The Bitcoin Well Affiliate and referral programs pay you automatically for your referral’s activities.
\ For example, today we have a 1.2% spread on standard portal transactions (buy, sell, pay bills). This means for every $100 someone spends on the platform we make $1.20, you’ll earn $0.24, automatically paid in sats. If they are using a Lite Account, with a 3% spread, you will earn $0.61 on that transaction, automatically paid in sats.
Referral bonuses don’t have an expiration date, cause we are all in bitcoin for the long haul!
The 21% revenue share for whales that end up purchasing through our OTC desk goes a long way, potentially in the thousands of referrals dollars per transaction. We do not place a cap on referral bonuses, so the bigger the whale, the bigger the referral bonus you earn!
How and when do I get paid?
Your referral bonuses are automatically paid out to the designated Lightning Wallet in your referral page. If you prefer, you can select a manual payout where you can withdraw your payouts at any time via LNURLw. \ \ OTC referral bonuses are processed around the middle of each month to your referral Lightning wallet.
What if I am not a fit for the Affiliate Program? Can I still earn from referrals?
Not everyone is the right fit for the Affiliate program, and that’s okay! Maintaining a far-reaching social presence is tough work. \ \ Thankfully, regular customers can still earn unlimited commissions from referrals at a 10% rate! This means for every $100 someone spends on the platform we make $1.20, you’ll earn $0.12, automatically paid in sats. The more your referrals transact, the more sats go to your Lightning wallet!
What makes Bitcoin Well different
Bitcoin Well is on a mission to enable independence. We do this by making it easy to self custody bitcoin. By custodying their own money, our customers are free to do as they wish without begging for permission. By creating a full ecosystem to buy, sell and use your bitcoin to connect with the modern financial world, you are able to have your cake and eat it too - or have your bitcoin in self custody and easily spend it too 🎂
Create your Bitcoin Well account now →
Invest in Bitcoin Well
We are publicly traded (and love it when our customers become shareholders!) and hold ourselves to a high standard of enabling life on a Bitcoin standard. If you want to learn more about Bitcoin Well, please visit our website!
-
 @ c0c42bba:a5feb7b5
2025-05-01 20:04:33
@ c0c42bba:a5feb7b5
2025-05-01 20:04:33Wisdom for the Fourth Decade
🔥
Turning 40 is like hitting the “I should really know better by now” milestone. It’s a time when you look back at your past self, shake your head, and chuckle (or cringe) at your youthful blunders.
Here are 15 truths you should embrace by this significant age, each one a guide to a more fulfilling, empowered life.
Leverage Is Key
Ever wonder why your colleague who seems to be on perpetual coffee breaks makes ten times more than you? It's not black magic. They have leverage—whether it's through technology, skills, or knowing how to delegate their way out of everything. Find your leverage and watch your value skyrocket.
Distraction: The Silent Killer
In our world of incessant notifications and cat videos, distraction is the enemy. It’s like having a mosquito in the room when you're trying to sleep. Cultivate a habit of deep work. Guard your attention like it's the last piece of cake at a party—fiercely.
Beware of Unqualified Advice
Taking advice from someone who hasn’t achieved what you want is like asking a cat for swimming lessons. Be selective with whose counsel you follow. Choose mentors who have walked the path and let their experiences be your map.
Own Your Life
Here’s the blunt truth: no one is coming to save you. Your problems, your life, are 100% your responsibility. Embrace this ownership. Empower yourself to be the hero of your own story. Don’t wait for a knight in shining armor—be your own rescue mission.
Action Over Self-Help Books
You don’t need to turn your living room into a self-help library. You need action. Self-discipline beats all the motivational quotes in the world. Commit to taking steps, however small, towards your goals. It's the doing, not just the knowing, that transforms dreams into reality.
The Power of Sales Skills
Unless your college degree is as specific as a neurosurgeon’s, your ticket to higher earnings in the next 90 days is learning sales. It’s a skill that opens doors, creates opportunities, and accelerates financial growth faster than you can say "commission."
No One Cares (In a Good Way)
Stop worrying about what others think—they’re too busy worrying about themselves. Take bold steps, make your moves, and create your chances. The world is too preoccupied with its own drama to scrutinize yours.
Collaborate with the Brilliant
When you meet someone smarter than you, don’t let your ego turn it into a competition. Collaborate with them. Two heads (especially two brilliant ones) are better than one, and together you can achieve remarkable things.
The Smoking Deception
Smoking has zero benefits. It’s like trying to improve your driving skills by riding a tricycle. If you want to sharpen your focus and enhance your thinking, ditch the habit. Your lungs—and your future self—will thank you.
Comfort: A Dangerous Addiction
Comfort is like quicksand. It feels nice until you’re stuck and can’t move. Regularly challenge yourself. Step out of your comfort zone because growth and fulfillment lie just beyond the boundaries of what feels easy.
Guard Your Privacy
Not everyone needs to know your life story, your plans, or what you had for breakfast. Maintain a sense of mystery. It’s not about being secretive; it’s about keeping some things just for yourself.
Alcohol: A Costly Vice
Alcohol impairs your judgment and lowers your inhibitions. It’s like paying someone to mess up your life. Avoid it. Clear thinking and control over your actions are priceless.
Keep Your Standards High
Don’t settle for less just because it’s available. High standards attract high-quality opportunities and people. Know your worth and hold out for what aligns with your values and goals.
Prioritize Your Chosen Family
The family you create is more important than the one you were born into. Nurture these relationships. They are your ride-or-die, your squad, your home team. Invest in them as they will be the cornerstone of your support system.
Take Nothing Personally
To save yourself from a myriad of mental burdens, learn not to take things personally. Most of the time, people’s actions are a reflection of their reality, not yours. This mindset shift will free you from unnecessary stress and emotional turmoil.
Embrace These Lessons -
 @ d34e832d:383f78d0
2025-04-26 07:17:45
@ d34e832d:383f78d0
2025-04-26 07:17:45Practical Privacy and Secure Communications
1. Bootable privacy operating systems—Tails, Qubes OS, and Whonix****
This Idea explores the technical deployment of bootable privacy operating systems—Tails, Qubes OS, and Whonix—for individuals and organizations seeking to enhance operational security (OpSec). These systems provide different layers of isolation, anonymity, and confidentiality, critical for cryptographic operations, Bitcoin custody, journalistic integrity, whistleblowing, and sensitive communications. The paper outlines optimal use cases, system requirements, technical architecture, and recommended operational workflows for each OS.
2. Running An Operating System
In a digital world where surveillance, metadata leakage, and sophisticated threat models are realities, bootable privacy OSs offer critical mitigation strategies. By running an operating system from a USB, DVD, or external drive—and often entirely in RAM—users can minimize the footprint left on host hardware, dramatically enhancing privacy.
This document details Tails, Qubes OS, and Whonix: three leading open-source projects addressing different aspects of operational security.
3. Technical Overview of Systems
| OS | Focus | Main Feature | Threat Model | |------------|---------------------------|-----------------------------------------------|--------------------------------| | Tails | Anonymity & Ephemerality | Runs entirely from RAM; routes traffic via Tor | For activists, journalists, Bitcoin users | | Qubes OS | Security through Compartmentalization | Hardware-level isolation via Xen hypervisor | Defense against malware, APTs, insider threats | | Whonix | Anonymity over Tor Networks | Split-Gateway Architecture (Whonix-Gateway & Whonix-Workstation) | For researchers, Bitcoin node operators, privacy advocates |
4. System Requirements
4.1 Tails
- RAM: Minimum 2 GB (4 GB recommended)
- CPU: x86_64 (Intel or AMD)
- Storage: 8GB+ USB stick (optional persistent storage)
4.2 Qubes OS
- RAM: 16 GB minimum
- CPU: Intel VT-x or AMD-V support required
- Storage: 256 GB SSD recommended
- GPU: Minimal compatibility (no Nvidia proprietary driver support)
4.3 Whonix
- Platform: VirtualBox/KVM Host (Linux, Windows, Mac)
- RAM: 4 GB minimum (8 GB recommended)
- Storage: 100 GB suggested for optimal performance
5. Deployment Models
| Model | Description | Recommended OS | |--------------------------|-----------------------------------|------------------------------| | USB-Only Boot | No installation on disk; ephemeral use | Tails | | Hardened Laptop | Full disk installation with encryption | Qubes OS | | Virtualized Lab | VMs on hardened workstation | Whonix Workstation + Gateway |
6. Operational Security Advantages
| OS | Key Advantages | |------------|----------------------------------------------------------------------------------------------------| | Tails | Memory wipe at shutdown, built-in Tor Browser, persistent volume encryption (LUKS) | | Qubes OS | Compartmentalized VMs for work, browsing, Bitcoin keys; TemplateVMs reduce attack surface | | Whonix | IP address leaks prevented even if the workstation is compromised; full Tor network integration |
7. Threat Model Coverage
| Threat Category | Tails | Qubes OS | Whonix | |----------------------------|-----------------|------------------|------------------| | Disk Forensics | ✅ (RAM-only) | ✅ (with disk encryption) | ✅ (VM separation) | | Malware Containment | ❌ | ✅ (strong) | ✅ (via VMs) | | Network Surveillance | ✅ (Tor enforced) | Partial (needs VPN/Tor setup) | ✅ (Tor Gateway) | | Hardware-Level Attacks | ❌ | ❌ | ❌ |
8. Use Cases
- Bitcoin Cold Storage and Key Signing (Tails)
- Boot Tails offline for air-gapped Bitcoin signing.
- Private Software Development (Qubes)
- Use separate VMs for coding, browsing, and Git commits.
- Anonymous Research (Whonix)
- Surf hidden services (.onion) without IP leak risk.
- Secure Communications (All)
- Use encrypted messaging apps (Session, XMPP, Matrix) without metadata exposure.
9. Challenges and Mitigations
| Challenge | Mitigation | |---------------------|---------------------------------------------| | Hardware Incompatibility | Validate device compatibility pre-deployment (esp. for Qubes) | | Tor Exit Node Surveillance | Use onion services or bridge relays (Tails, Whonix) | | USB Persistence Risks | Always encrypt persistent volumes (Tails) | | Hypervisor Bugs (Qubes) | Regular OS and TemplateVM updates |
Here’s a fully original technical whitepaper version of your request, rewritten while keeping the important technical ideas intact but upgrading structure, language, and precision.
Executive Summary
In a world where digital surveillance and privacy threats are escalating, bootable privacy operating systems offer a critical solution for at-risk individuals. Systems like Tails, Qubes OS, and Whonix provide strong, portable security by isolating user activities from compromised or untrusted hardware. This paper explores their architectures, security models, and real-world applications.
1. To Recap
Bootable privacy-centric operating systems are designed to protect users from forensic analysis, digital tracking, and unauthorized access. By booting from an external USB drive or DVD and operating independently from the host machine's internal storage, they minimize digital footprints and maximize operational security (OpSec).
This paper provides an in-depth technical analysis of: - Tails (The Amnesic Incognito Live System) - Qubes OS (Security through Compartmentalization) - Whonix (Anonymity via Tor Isolation)
Each system’s strengths, limitations, use cases, and installation methods are explored in detail.
2. Technical Overview of Systems
2.1 Tails (The Amnesic Incognito Live System)
Architecture:
- Linux-based Debian derivative. - Boots from USB/DVD, uses RAM exclusively unless persistent storage is manually enabled. - Routes all network traffic through Tor. - Designed to leave no trace unless explicitly configured otherwise.Key Features:
- Memory erasure on shutdown. - Pre-installed secure applications: Tor Browser, KeePassXC, OnionShare. - Persistent storage available but encrypted and isolated.Limitations:
- Limited hardware compatibility (especially Wi-Fi drivers). - No support for mobile OS platforms. - ISP visibility to Tor network usage unless bridges are configured.
2.2 Qubes OS
Architecture:
- Xen-based hypervisor model. - Security through compartmentalization: distinct "qubes" (virtual machines) isolate tasks and domains (work, personal, banking, etc.). - Networking and USB stacks run in restricted VMs to prevent direct device access.Key Features:
- Template-based management for efficient updates. - Secure Copy (Qubes RPC) for data movement without exposing full disks. - Integrated Whonix templates for anonymous browsing.Limitations:
- Requires significant hardware resources (RAM and CPU). - Limited hardware compatibility (strict requirements for virtualization support: VT-d/IOMMU).
2.3 Whonix
Architecture:
- Debian-based dual VM system. - One VM (Gateway) routes all traffic through Tor; the second VM (Workstation) is fully isolated from the physical network. - Can be run on top of Qubes OS, VirtualBox, or KVM.Key Features:
- Complete traffic isolation at the system level. - Strong protections against IP leaks (fails closed if Tor is inaccessible). - Advanced metadata obfuscation options.Limitations:
- High learning curve for proper configuration. - Heavy reliance on Tor can introduce performance bottlenecks.
3. Comparative Analysis
| Feature | Tails | Qubes OS | Whonix | |:--------|:------|:---------|:-------| | Anonymity Focus | High | Medium | High | | System Isolation | Medium | Very High | High | | Persistence | Optional | Full | Optional | | Hardware Requirements | Low | High | Medium | | Learning Curve | Low | High | Medium | | Internet Privacy | Mandatory Tor | Optional Tor | Mandatory Tor |
4. Use Cases
| Scenario | Recommended System | |:---------|:--------------------| | Emergency secure browsing | Tails | | Full system compartmentalization | Qubes OS | | Anonymous operations with no leaks | Whonix | | Activist communications from hostile regions | Tails or Whonix | | Secure long-term project management | Qubes OS |
5. Installation Overview
5.1 Hardware Requirements
- Tails: Minimum 2GB RAM, USB 2.0 or higher, Intel or AMD x86-64 processor.
- Qubes OS: Minimum 16GB RAM, VT-d/IOMMU virtualization support, SSD storage.
- Whonix: Runs inside VirtualBox or Qubes; requires host compatibility.
5.2 Setup Instructions
Tails: 1. Download latest ISO from tails.net. 2. Verify signature (GPG or in-browser). 3. Use balenaEtcher or dd to flash onto USB. 4. Boot from USB, configure Persistent Storage if necessary.
Qubes OS: 1. Download ISO from qubes-os.org. 2. Verify using PGP signatures. 3. Flash to USB or DVD. 4. Boot and install onto SSD with LUKS encryption enabled.
Whonix: 1. Download both Gateway and Workstation VMs from whonix.org. 2. Import into VirtualBox or a compatible hypervisor. 3. Configure VMs to only communicate through the Gateway.
6. Security Considerations
- Tails: Physical compromise of the USB stick is a risk. Use hidden storage if necessary.
- Qubes OS: Qubes is only as secure as its weakest compartment; misconfigured VMs can leak data.
- Whonix: Full reliance on Tor can reveal usage patterns if used carelessly.
Best Practices: - Always verify downloads via GPG. - Use a dedicated, non-personal device where possible. - Utilize Tor bridges if operating under oppressive regimes. - Practice OPSEC consistently—compartmentalization, metadata removal, anonymous communications.
7. Consider
Bootable privacy operating systems represent a critical defense against modern surveillance and oppression. Whether for emergency browsing, long-term anonymous operations, or full-stack digital compartmentalization, solutions like Tails, Qubes OS, and Whonix empower users to reclaim their privacy.
When deployed thoughtfully—with an understanding of each system’s capabilities and risks—these tools can provide an exceptional layer of protection for journalists, activists, security professionals, and everyday users alike.
10. Example: Secure Bitcoin Signing Workflow with Tails
- Boot Tails from USB.
- Disconnect from the network.
- Generate Bitcoin private key or sign transaction using Electrum.
- Save signed transaction to encrypted USB drive.
- Shut down to wipe RAM completely.
- Broadcast transaction from a separate, non-sensitive machine.
This prevents key exposure to malware, man-in-the-middle attacks, and disk forensic analysis.
11. Consider
Bootable privacy operating systems like Tails, Qubes OS, and Whonix offer robust, practical strategies for improving operational security across a wide spectrum of use cases—from Bitcoin custody to anonymous journalism. Their open-source nature, focus on minimizing digital footprints, and mature security architectures make them foundational tools for modern privacy workflows.
Choosing the appropriate OS depends on the specific threat model, hardware available, and user needs. Proper training and discipline remain crucial to maintain the security these systems enable.
Appendices
A. Download Links
B. Further Reading
- "The Qubes OS Architecture" Whitepaper
- "Operational Security and Bitcoin" by Matt Odell
- "Tor and the Darknet: Separating Myth from Reality" by EFF
-
 @ fdd4dcaf:34a25ae0
2025-05-01 18:58:20
@ fdd4dcaf:34a25ae0
2025-05-01 18:58:20Cryptocurrency is a digital or virtual currency that uses cryptography for security and is decentralized, meaning it's not controlled by any government or financial institution.
Key Features 1. Decentralized: Cryptocurrencies operate independently of central banks and governments. 2. Digital: Cryptocurrencies exist only in electronic form. 3. Secure: Cryptocurrencies use advanced cryptography for secure transactions. 4. Limited supply: Most cryptocurrencies have a limited supply, which can help maintain their value.
Popular Cryptocurrencies 1. Bitcoin (BTC): The first and most well-known cryptocurrency. 2. Ethereum (ETH): A popular platform for decentralized applications (dApps). 3. Other altcoins: Litecoin, Ripple, Dogecoin, and many more.
Uses 1. Payments: Cryptocurrencies can be used for online transactions. 2. Investments: Some people invest in cryptocurrencies as a store of value or for potential growth. 3. Decentralized applications: Cryptocurrencies can power dApps and smart contracts.
Risks and Challenges 1. Volatility: Cryptocurrency prices can fluctuate rapidly. 2. Security risks: Cryptocurrency exchanges and wallets can be vulnerable to hacking. 3. Regulatory uncertainty: Cryptocurrency regulations vary by country and are subject to change.
-
 @ 04ea4f83:210e1713
2025-05-01 18:22:24
@ 04ea4f83:210e1713
2025-05-01 18:22:2430. November 2022
Sehr geehrter Herr Bindseil und Herr Schaff von der Europäischen Zentralbank,
Ich schreibe Ihnen heute, am Tag der Veröffentlichung Ihres EZB-Blog-Berichts „Bitcoin's Last Stand", sowohl mit Belustigung als auch mit Bestürzung. Ich amüsiere mich darüber, wie albern und hilflos Sie beide erscheinen, indem Sie sich auf müde und längst widerlegte Erzählungen über Bitcoin und seine Nutzlosigkeit und Verschwendung stützen. Und ich bin beunruhigt, weil ich von zwei sehr gut ausgebildeten und etablierten Mitgliedern Ihres Fachgebiets eine viel differenziertere kritische Sichtweise auf den aufkeimenden Bitcoin und die Lightning Skalierungslösung erwartet hätte.
Sie haben sich mit Ihren dilettantischen Versuchen, Angst, Unsicherheit und Zweifel an einem globalen Open-Source-Kooperationsprojekt zu säen, das als ein ständig wachsendes Wertspeicher und -übertragungssystem für viele Millionen Menschen weltweit fungiert, wirklich einen Bärendienst erwiesen. Ein System, das jedes Jahr von mehr und mehr Menschen genutzt wird, da sie von seiner Effektivität und seinem Nutzen erfahren. Und ein System, das noch nie gehackt oder geknackt wurde, das funktioniert, um die „Banklosen" zu versorgen, besonders in den Ländern und Orten, wo sie von finsteren totalitären Regierungen schwer unterdrückt oder von der finanziell „entwickelten" Welt einfach im Stich gelassen wurden. In der Tat ist Bitcoin bereits gesetzliches Zahlungsmittel in El Salvador und der Zentralafrikanischen Republik, und erst gestern erhielt er in Brasilien den Status eines „Zahlungsmittels".
Es entbehrt nicht einer gewissen Ironie, wenn ich schreibe, dass Sie das Ziel so gründlich verfehlen, insbesondere weil die Bank- und Finanzsysteme, zu denen Sie gehören, für eine Energie- und Materialverschwendung verantwortlich sind, die um Größenordnungen größer ist als die Systeme und Ressourcen, die das Bitcoin-Netzwerk antreiben und erhalten. Ich bin mir sicher, dass Sie sich der revolutionären kohlenstoff- und treibhausgasreduzierenden Effekte bewusst sind, die Bitcoin-Mining-Anlagen haben, wenn sie neben Methan-emittierenden Mülldeponien und/oder Ölproduktionsanlagen angesiedelt sind. Und ich weiß, dass Sie auch gut über solar- und windbetriebene Bitcoin-Mining-Cluster informiert sind, die dabei helfen, Mikronetze in unterversorgten Gemeinden einzurichten.
Ich könnte noch weiter darüber sprechen, wie das Lightning-Netzwerk implementiert wird, um Überweisungszahlungen zu erleichtern sowie Finanztechnologie und Souveränität in Gemeinden in Laos und Afrika südlich der Sahara zu bringen. Aber lassen Sie mich zu dem Teil kommen, der einen gewöhnlichen Menschen wie mich einfach zutiefst traurig macht. Bitcoin ist, wie Sie sehr wohl wissen (trotz Ihrer dummen und veralteten Verleumdungen), ein technologisches Netzwerk, das nicht auf nationaler oder internationaler Verschuldung oder der Laune von Politikern basiert oder durch sie entwertet wird. Es ist ein System, das jenseits der Kontrolle einer einzelnen Person, eines Landes oder einer Gruppe von Ländern liegt. Wenn Bitcoin sprechen könnte (was er in der Tat ungefähr alle zehn Minuten tut, durch das elektro-mathematische Knistern und Summen des Wahrheitsfeuers), würde er diese Worte aussprechen:
„Über allen Völkern steht die Menschlichkeit".\ \ Als Bankiers der Europäischen Union, als Menschen von der Erde, als biologische Wesen, die denselben Gesetzen des Verfalls und der Krankheit unterliegen wie alle anderen Wesen, wäre es da nicht erfrischend für Sie beide, das Studium und die Teilnahme an einer Technologie zu begrüßen, die die Arbeit und die Bemühungen der sich abmühenden Menschen auf unserem Planeten bewahrt, anstatt sie zu entwerten? Wie die Bitcoin-Kollegin Alyse Killeen wiederholt gesagt hat: „Bitcoin ist FinTech für arme Menschen".
Ich bin dankbar für Ihre Aufmerksamkeit und hoffe, dass Sie über Bitcoin nachdenken und es gründlicher studieren werden.
Mit freundlichen Grüßen,
Cosmo Crixter
-
 @ 04ea4f83:210e1713
2025-05-01 18:21:07
@ 04ea4f83:210e1713
2025-05-01 18:21:07Erschienen in Citadel21 Vol. 18 | Veröffenlichung 21. Juli 2022\ Autor: FractalEncrypt\ Übersetzt von: Sinautoshi am 15.12.2022 - 767561

„Hast du das Recht, deinen eigenen Verstand zu verändern? Hast du das Recht, deinen eigenen Computer zu verändern? Was sind deine Rechte, und was sind deine eigenen? Was sind die Grenzen der Gesellschaft und was sind die Grenzen des Einzelnen?" - Kevin Paul Herbert
Bitcoin und Psychedelika sind gleichzeitig die mächtigsten, aber am wenigsten verstandenen Technologien auf dem Planeten.
\ Sie ergänzen sich zu revolutionären Technologien, die für ein tiefgreifendes persönliches Wachstum genutzt werden können. Sie helfen uns, selbstbestimmte Grenzen in unserem Leben zu definieren, wenn es um die Frage geht, wer die Herrschaft über die Dinge hat, die wir denken, die Software, die wir benutzen, und die Handlungen, die wir ausführen. Sie können dazu genutzt werden, die Zukunft des Einzelnen und damit auch die der Welt zu gestalten. Viele nutzen diese Werkzeuge heute, um ein besseres, produktiveres Leben zu führen. Sowohl Psychedelika als auch Bitcoin bewirken einen Paradigmenwechsel bei den Nutzern. Das sind keine einfachen Veränderungen. Diese grundlegenden und dauerhaften Veränderungen können die Art und Weise, wie man mit der Welt interagiert, völlig verändern. Souveräne Menschen können sie nutzen, um auf messbare und unermessliche, materielle und immaterielle Weise zu großem Reichtum zu gelangen. Wie bei jedem Werkzeug gibt es auch hier Gefahren, aber der richtige Gebrauch in Verbindung mit Sinn und Verstand führt zu den besten Ergebnissen.
Wie bei allen Werkzeugen sind auch diese nicht für jeden geeignet.
\ Während sowohl Bitcoin als auch Psychedelika stark missverstanden werden, können diejenigen, die sich mit kontemplativen Studien beschäftigen, asymmetrische Gewinne erzielen. Fast niemand versteht vollständig, wie diese Dinge funktionieren, nicht einmal diejenigen, die sie regelmäßig besitzen oder nutzen. Ich kann das nicht genug betonen. Selbst Menschen mit Erfahrung haben Schwierigkeiten, das Ausmaß dieser Technologien vollständig zu erfassen. Jameson Lopp, einer der ersten Bitcoin-Entwickler, sagt: „Niemand versteht Bitcoin, und das ist auch gut so". Das Gleiche gilt für Psychedelika. Die Entscheidung, sich mit diesen Technologien zu beschäftigen, ist eine sehr persönliche Entscheidung, die man nicht auf die leichte Schulter nehmen sollte. Wenn du dir die Zeit nimmst, dich eingehend mit diesen Technologien zu befassen, gehörst du zu dem kleinen Prozentsatz der Bevölkerung, der sie verstehen möchte und davon profitieren kann. Jeder muss dies für sich selbst entscheiden, und das gilt hier mehr als anderswo - Wissen ist Macht.

Einführung
\ Es gibt erstaunlich viele Beziehungen zwischen Bitcoin und Psychedelika, die sich auf vielen verschiedenen Ebenen ergeben. Diese Ähnlichkeiten führen zu einer tiefer gehenden Frage:
Sind Bitcoin und Psychedelika Werkzeuge der Selbstsouveränität, weil sie diese Ähnlichkeiten haben, oder sind sie ähnlich, weil sie Werkzeuge der Selbstsouveränität sind?
Um die Antwort zu finden, müssen wir die beiden Werkzeuge einzeln und in Kombination untersuchen. In diesem Artikel gehen wir auf die vielen Ebenen der Übereinstimmung zwischen diesen Technologien ein und ich möchte dich ermutigen, tiefer eizusteigen, wenn dein Interesse geweckt ist. Diese Kaninchenlöcher gehen tief.
Wie bei Bitcoin ist der LSD- und Psilocybin-Quellcode in verschiedenen Implementierungen frei verfügbar. Die Schöpfer von LSD und Bitcoin haben Anleitungen veröffentlicht, damit jeder auf der ganzen Welt die jeweiligen Tools lesen, verstehen und nutzen kann. Jeder kann das LSD-Patent mit den genauen Schritten zur Synthese von reinem LSD frei lesen, und jeder kann den Bitcoin-Quellcode frei lesen und seine eigene Software von Grund auf erstellen. Jeder kann an jedem Ort seine eigene Implementierung erstellen und sich einem bereits weltweit vernetzten Netzwerk von Gleichgesinnten anschließen. Die Werkzeuge sind weithin verfügbar und können von interessierten Bastlern zu Hause aus einer erstaunlichen Anzahl von Standardteilen hergestellt werden. Wenn sie erst einmal installiert sind, kann eine vorsichtige und aufmerksame Person diese Werkzeuge mit großem Nutzen einsetzen. Eine unvorsichtige Nutzung wird schnell und entschieden bestraft, und die Nutzer müssen sich selbst verbessern, nachdem sie ihre Lektion auf die harte Tour gelernt haben. Konsequenzen sind ein fester Bestandteil von Systemen, die Verantwortung verlangen.
Der ehrliche Forscher wird in Bezug auf diese beiden Technologien von Desinformationen geplagt. Bei den Psychedelika gibt es eine endlose Reihe von falschen Behauptungen. Sie reichen von „Chromosomenschäden, die zu missgebildeten Babys führen" bis hin zu „du springst aus dem Fenster und glaubst, du kannst fliegen" oder sogar, dass du „von einer einzigen Dosis dauerhaft verrückt werden kannst". Es gibt auch eine endlose Reihe von falschen Behauptungen über Bitcoin, von staatlichen Eingriffen über den Verbrauch von mehr Energie als Land X bis hin zum Kochen der Ozeane oder „es ist eine langsame, veraltete Technologie". Deshalb müssen unerschrockene Reisende ihre Bullshit-Detektoren schärfen und Experten in Sachen Recherche und logischem Denken werden.
Die Wahrheit ist, dass die Propagandamauern rund um Bitcoin und Psychedelika errichtet wurden, um die Menschen davon abzulenken, sich selbst zu versorgen. Nachgiebige Menschen, die keine Fragen stellen, sind viel leichter zu kontrollieren als Menschen, die für ihre Freiheit eintreten. Ein Großteil der Anti-Psychedelika- und Anti-Bitcoin-Propaganda kommt direkt von der Regierung. Die Fehlinformationen werden in einen Mantel der Seriosität gehüllt und durchdringen schnell die Gesellschaft. Wenn du Medien oder Inhalte konsumierst, schau dir immer die Quelle an. Wer stellt diese Informationen zur Verfügung und zu welchem Zweck? Achte immer auf die Beweggründe und Anreize. Benutze die „Brille des Skeptikers", wenn du diese Instrumente untersuchst. Glaube keiner Behauptung (auch nicht meiner), ohne sie zu belegen und zu dokumentieren. Vertraue nicht, sondern überprüfe.
Während sowohl Psychedelika als auch Bitcoin in den Mainstream-Medien als gefährlich, schädlich und geradezu böse verteufelt wurden, möchte ich hier dafür plädieren, dass diese Dinge gesund sind, gute Familienwerte vermitteln und mächtige Werkzeuge sind, um uns selbst und unsere Beziehungen zu anderen und der Welt zu verändern.
Auch wenn Bitcoin und Psychedelika wertvolle Werkzeuge sein können, sind sie kein Gegenmittel für falsches Denken. Während einige Nutzer diese Werkzeuge nutzen können, um zu handlungsrelevanten Erkenntnissen zu gelangen, sind nicht alle Nutzer so erfolgreich. Diejenigen, die sich von falschem Denken leiten lassen, können sich in den Seitengassen von Shitcoinerei, New-Age-Zauberkram und anderen logischen Irrtümern wiederfinden. Anstatt diese Wege als destruktiv zu erkennen, gaukeln sie sich vor, etwas Revolutionäres entdeckt zu haben. Es ist wichtig, dass du dein bestes Urteilsvermögen einsetzt und eine skeptische Haltung bewahrst, wenn du dich im Leben im Allgemeinen und mit diesen Tools im Besonderen bewegst.
Die Vorteile, die eine bessere Integration dieser Technologien in die moderne Gesellschaft mit sich bringt, sind enorm und könnten die Zukunft der Menschheit auf tiefgreifende Weise verändern.
Bitcoin ermöglicht eine vernetzte Welt mit einer einzigen Währung. Wie die Verwendung einer einzigen Sprache bringt er uns mit einem fließenden und dynamischen globalen Zusammenhalt zusammen. Handel, Reisen, Umzüge, Steuern und Währungsumrechnung. All das wird durch eine bescheidene Technologie vereinfacht, die für alle zugänglich ist.
Für Psychedelika kann die Integration viele Wege gehen. Der hoffnungsvollste ist jedoch der, bei dem die Menschen legalen Zugang zu bekannten Molekülen in bekannter Reinheit und mit verlässlichen Informationen über deren sichere Verwendung haben. Die Schaffung von sicheren Räumen für den Konsum von Psychedelika (wie die temporären autonomen Zonen von Hakim Bey) und ihre Verknüpfung mit psychedelischen Krisenzentren, die an lokalen Universitäten untergebracht sind, würde es der Gesellschaft ermöglichen, von beiden Seiten der psychedelischen Erfahrung zu profitieren. Die Kreativität und Fantasie der autonomen Räume und die Heilung und Transformation, die durch die Betreuung von Menschen in einer psychedelischen Krise möglich sind, haben ein grenzenloses Potenzial. Dieses sorgfältige Erfahrungsmanagement würde dem Nutzer, den Betreuern und der Gesellschaft insgesamt zugute kommen. Die durchdachte Integration dieser beiden Technologien in die moderne Gesellschaft hat das Potenzial, sowohl dem Einzelnen als auch der globalen Gemeinschaft Vorteile zu bringen.
Bildgebende Studien des Gehirns unter Einfluss von LSD und Psilocybin geben interessante Hinweise darauf, dass Psychedelika die Gehirnaktivität erhöhen und neue Bahnen und Verbindungen im gesamten Gehirn aktivieren. Wenn das mit dem Einzelnen passiert, stell dir vor, was mit dem Makrokosmos der Zivilisation passiert.
Jeder Weg birgt Gefahren, und es gibt kein Patentrezept. Wir haben die Werkzeuge; sie mit Geschick, Integrität und Zielstrebigkeit einzusetzen, ist eine Entscheidung. Das Werkzeug wird die Arbeit nicht für dich erledigen. Das ist der Proof of Work-Gedanke in Aktion.
Ein Hinweis zu den hier erwähnten psychedelischen Substanzen: Es gibt zwar viele psychedelische Verbindungen, aber in diesem Artikel konzentriere ich mich auf LSD und Psilocybin. LSD ist zwar das am weitesten verbreitete Psychedelikum, aber es kann eine zentralisierende Wirkung auf die Chemiker haben, die es herstellen. Es bildet sich eine natürliche Vertriebspyramide mit dem Chemiker an der Spitze, den Groß- und Einzelhändlern und schließlich den Endverbrauchern, die die Basis der Pyramide bilden. Diese Pyramide entsteht, weil ein einziges Gramm LSD 10.000 Dosen enthält. Die LSD-Synthese ist für begeisterte Forscher nicht unerreichbar, aber für den „Normalbürger" nicht so leicht zugänglich wie der Anbau von Pilzen. Pilze der Gattung Psilocybe sind viel dezentraler, weil sie ein Werkzeug sind, das von fast jedem und überall auf dem Planeten eingesetzt werden kann. Es wird kein Händler benötigt, nur du, etwas Erde und ein paar Sporen.
Zusammensetzung der Leserschaft
\ Ich gehe davon aus, dass dieser Artikel von Personen mit unterschiedlichem Verständnis für die behandelten Themen gelesen wird. Ich gehe davon aus, dass die Leser in eine der folgenden vier Kategorien fallen;
- Bitcoiner, die Erfahrung mit Psychedelika haben
- Bitcoiners, die keine Erfahrung mit Psychedelika haben
- Menschen mit psychedelischer Erfahrung, die Bitcoin nicht benutzen
- Menschen, die weder mit dem einen noch mit dem anderen Erfahrung haben
Während sich der größte Teil dieses Artikels auf die Vergleiche und Gemeinsamkeiten zwischen Bitcoin und Psychedelika konzentriert, gehen die folgenden kurzen Abschnitte auf jeden einzelnen ein. Für diejenigen, die damit nicht vertraut sind, beschreibe ich kurz, warum ich beide für ein wichtiges Instrument der Selbstbestimmung halte. Sowohl Bitcoin als auch Psychedelika sind Gegenstand von wilden Fehlinformationskampagnen, auf die wir später noch genauer eingehen werden. Ich erwähne das jetzt nur, um darauf hinzuweisen, dass die allgemein zugänglichen Medien zu beiden Themen verwirrend und in vielerlei Hinsicht irreführend sind, wenn du nur ein oberflächliches Verständnis von beiden Themen hast. Man muss sich eingehend mit dem Thema befassen, um den ganzen Schwachsinn zu durchschauen.
Für diejenigen, die noch keine Erfahrung mit Psychedelika haben oder diese nicht kennen
\ LSD und Psilocybin gehören zu den mächtigsten Werkzeugen für die Selbsterkundung, die heute verfügbar sind. Sie sind außerdem ungiftig und nicht gewohnheitsbildend, obwohl sie auch Gefahren bergen. Sie geben dir einen Zugang zu dir selbst, den du auf keine andere Weise erreichen kannst. Kein noch so großer Yoga- oder Meditationstrip kann dir einen LSD-Trip bescheren. Sie gehören zu den sichersten Moleküle auf dem Planeten. Vergleiche zum Beispiel NULL Todesfälle durch LSD und Magic Mushrooms mit über 3.000 Todesfällen pro Jahr durch etwas, das als sicher gilt, wie Aspirin.
Die Bedeutung von Psychedelika als Mittel zur menschlichen Selbsterforschung kann gar nicht hoch genug eingeschätzt werden. Steve Jobs beschrieb die Einnahme von LSD als eines der wichtigsten Dinge in seinem Leben.
"Die Einnahme von LSD war eine tiefgreifende Erfahrung, eines der wichtigsten Dinge in meinem Leben. Es stärkte meinen Sinn für das, was wichtig war - großartige Dinge zu schaffen und sie in den Strom der Geschichte und des menschlichen Bewusstseins einzubringen, so gut ich konnte." - Steve Jobs
\ Roland Griffiths Arbeit an der Johns Hopkins University zeigt, dass Psilocybin Depressionen und Angstzustände bei Patienten mit lebensbedrohlichen Krebserkrankungen erheblich und nachhaltig verringert.
„Das hat mich wie ein Schlag ins Gesicht getroffen. Die Vorstellung, dass Menschen Psilocybin einnehmen und sich ihr Leben innerhalb weniger Stunden komplett verändert. Nicht nur positive Veränderungen von Einstellungen, Verhaltensweisen und Überzeugungen, sondern eine grundlegende psychologische Veränderung an einem Nachmittag. Selbst einige Jahre nach den Experimenten berichten 75 % der Freiwilligen, dass ihre einzige Psilocybin-Dosis eine der bedeutsamsten Erfahrungen ihres Lebens war, wenn nicht sogar DIE bedeutsamste Erfahrung überhaupt."\ - Brian Muraresku

Für alle, die neu sind oder keine Erfahrung mit Bitcoin haben
\ Bitcoin ist eine Null-zu-Eins-Erfindung, die den Regierungen der Welt die Macht entzieht und sie an Einzelpersonen zurückgibt. Es ist eine nie wieder zu wiederholende Entdeckung, die seit einem Jahrzehnt das Leben verändert. Es ist Geld, das durch Mathematik gestützt wird, nicht durch die Versprechen von Politikern.
Hast du dich jemals gefragt, ob Geld für die menschliche Entwicklung und das Wachstum wichtig ist? Wie haben verschiedene Formen von Geld den Verlauf der menschlichen Geschichte verändert? Geld wird gegen die Zeit der Menschen getauscht. Unsere Lebenszeit ist endlich. Eine unendliche Ressource zu verwenden, um für eine endliche Ressource zu bezahlen, ist von Natur aus ungerecht. Im Geld ist Lebensenergie gespeichert.
Das Geld, das wir heute verwenden, ist als Fiat-Geld bekannt, „Geld per Dekret". Mit anderen Worten: „Geld, weil wir es sagen". Fiat-Geld verliert mit der Zeit an Wert, was als „Inflationsrate" bezeichnet wird. Geld, das mit der Zeit an Wert verliert, ist Zeitdiebstahl. Es stiehlt den Wert, für den du bereits gearbeitet und deine Zeit und Energie investiert hast, um ihn zu verdienen. Bitcoin ist Geld, das im Laufe der Zeit nie an Wert verliert. Seine elegante mathematische Ausschüttung ist vorprogrammiert und unveränderlich.
„Du kannst beim Fiat-Standard bleiben, bei dem einige Leute kostenlos unbegrenzt neue Geldeinheiten produzieren können, nur du nicht. Oder du kannst dich für den Bitcoin-Standard entscheiden, bei dem niemand das tun darf, auch du nicht."- Ross Stevens

\ Auch wenn ich keine begutachteten Studien vorweisen kann, habe ich als persönliche Anekdote eine Unterströmung der Selbstverwirklichung bemerkt, die sich stark durch die Bitcoin-Kultur zieht. Viele setzen sich für eine Rückbesinnung auf das Landleben ein, für eine gesunde Ernährung (indem sie schlechte Lebensmittel wie Samenöle und künstliches Fleisch weglassen und sich vermehrt mit minimal oder gar nicht verarbeiteten natürlichen Lebensmitteln ernähren), für Sport, Kunst, Familie und Wellness.
Ich glaube, dass das persönliche Wachstum der Bitcoiner die Ethik widerspiegelt, die im Bitcoin-Netzwerk selbst einprogrammiert ist. Hier sind zwei Beispiele;
Proof of Work - Bitcoinern ist klar, dass ohne Handeln kein Wert geschaffen werden kann. Das gilt für fast jeden Aspekt des Lebens. Um die Vorteile zu erhalten, muss man die Arbeit machen.
Vertraue nicht, sondern verifiziere (Don't Trust, Verify) - der Aspekt des Verifizierens und nicht nur des Akzeptierens jeder angebotenen Version der Wahrheit ist heute wichtiger denn je.
Es gibt noch viel mehr, aber ich hoffe, dass dieser kurze Überblick einen Einblick gibt, warum diese beiden Technologien meiner Meinung nach komplementär und diskussionswürdig sind.
Werkzeuge der Selbstbestimmung
\ Wenn ich sage, dass Bitcoin und Psychedelika Werkzeuge der Selbstbestimmung sind, dann will ich damit sagen, dass es sich um Werkzeuge handelt, die jedem von uns heute zur Verfügung stehen und die wir nutzen können, um unsere eigenen Antworten auf Fragen wie diese zu definieren, zu formen und zu gestalten:
- Was bedeutet es, ein freies und souveränes Individuum zu sein?
- Was darf der Staat regeln?
- Was sind deine Rechte, und was ist dein Eigentum?
- sind die Grenzen der Gesellschaft und
- was sind die Grenzen des Individuums?
- Hast du das Recht, deine eigene Meinung zu ändern?
- Hast du das Recht, deinen eigenen Computer zu verändern?
Unsere Antworten auf Fragen wie diese bestimmen den Verlauf unseres Lebens. Wir können diese Werkzeuge nutzen, um tiefer in unseren Geist und Körper zu blicken oder an die Grenzen des Verständnisses zu gelangen. Der zielstrebige Mensch kann diese Erkenntnisse nutzen, um ein erfolgreicheres Leben zu führen.
Bitcoin ist ein Werkzeug der Information. LSD ist ein Mittel der Erfahrung und der Vorstellungskraft.
Die grünen Rechtecke aus Fiat-Papier haben einen Wert, weil der Staat das sagt. Bitcoin ist das Gegengift zum Fiat-Geld. Vieles andere auf dieser Welt wird uns per Dekret aufgezwungen. Bitcoin hilft dir, Fiat-Geld aus deinem Leben zu entfernen. Psychedelika helfen dir, Fiat-Geld aus deinem Geist und Körper zu entfernen. Zusammen geben sie dir die Macht, in deiner Souveränität aufrecht zu stehen und die ultimative Herrschaft über dein inneres und äußeres Leben zu erlangen.
Es sind Werkzeuge, die wir zu Hause für unseren persönlichen Gebrauch nutzen können und die niemandem schaden. Psychedelika, manchmal auch Entheogene genannt, wecken ein Gefühl für das Göttliche im Inneren. Sie geben den Nutzern direkten Zugang zu mystischen Zuständen, ohne dass Dritte wie organisierte Religionen, Schriften oder Doktrinen dazwischengeschaltet werden müssen. Bitcoin bietet den Nutzern Zugang zu Geld, das durch Mathematik gestützt wird und nicht durch die Versprechen von Ökonomen, Banken oder Politikern. Die Nutzer sind nicht gezwungen, Vermittler zwischen sich und die direkte Erfahrung der Realität zu stellen. Sie sind nicht gezwungen, sich von jemand anderem sagen zu lassen, „wie es ist" oder „wie es sich anfühlt". Sie können es selbst erleben.
Bei Bitcoin haben alle Nutzer die Möglichkeit, einen vollständigen Knotenpunkt (Full-Node) zu betreiben, und damit direkten Zugang zu einem weltweit vernetzten Finanznetzwerk ohne Vermitter oder Zensur. Bei Psychedelika erhalten die Nutzer einen direkten, unvermittelten Zugang zu ihren eigenen vernetzten neuronalen Netzwerken. Es gibt auch global vernetzte soziale Netzwerke, die entstehen, um beide Technologien zu verbreiten, zu diskutieren und zu nutzen, oft in Kombination. Das sind Peer-to-Peer-Netzwerke ohne Anführer, ohne Verantwortliche und ohne Angestellte. Alle Nutzer sind gleichberechtigt.
Die Verwendung von Bitcoin und Psychedelika eröffnet das Verständnis für die Verflechtung verschiedener Disziplinen und Technologien. Politik, Technik, Wirtschaft, Chemie, Psychologie, Spieltheorie, Soziologie und Philosophie sind nur einige der Bereiche, die zusammenkommen, um unser Verständnis für diese Werkzeuge und ihre optimale Nutzung zu verbessern.
Viele Nutzerinnen und Nutzer von Bitcoin und Psychedelika haben festgestellt, dass der Weg zu einem tieferen Verständnis in einer breiten Palette von Themen liegt. Die Kombination des durch Bildung gewonnenen Wissens mit den Erkenntnissen, die wir durch die Nutzung dieser Technologien gewinnen, bringt mehr Tiefe und Verständnis in unser Leben.
„Bitcoin ist amoralisch und absolut neutral gegenüber der Frage, ob du dem Netzwerk beitrittst oder nicht", sagt Mark Maraia. Ich würde das noch erweitern und sagen, dass LSD amoralisch und absolut neutral ist. Die extremen Erfahrungen sind auf deine persönliche Körperchemie, deine Einstellung und das gesamte Wissen und die Erfahrung deines Lebens zurückzuführen. Wir sind die Variablen, Bitcoin und LSD sind die Konstanten. Du bekommst das heraus, was du hineinbringst.
Ich habe viele Bitcoiner gesehen, die in Kaninchenlöcher geraten sind, die zu bedeutenden Veränderungen in ihrem Leben führen. Wie sie essen, arbeiten, Sport treiben, Medien konsumieren und vieles mehr, ändert sich. Tiefgreifende Veränderungen, die sie oft dem Bitcoin und dem Grundsatzdenken zuschreiben. Diese Lebensveränderungen haben wenig oder gar nichts mit Wirtschaft, Geld oder Finanzen zu tun.
Nutzer von Psychedelika machen ähnliche Veränderungen in ihrem Lebensstil durch, die ihren Umgang mit der Welt tiefgreifend verändern. Diese Veränderungen können sich auf die gleiche Weise wie beim Bitcoin manifestieren: Sie verändern die Art und Weise, wie Menschen essen, arbeiten, Sport treiben, Medien konsumieren, miteinander interagieren, usw. Diese bedeutenden Veränderungen im Leben wären ohne den direkten Einsatz einer oder beider der in diesem Artikel besprochenen Technologien vielleicht nie verwirklicht worden.
Wie jedes Werkzeug kann auch dieses missbraucht werden und die Nutzer auf den falschen Weg führen. Wir werden in Kürze mehr über die naiven Irregeleiteten, die Affinitätsbetrüger, die Angreifer und die ganz schlechten Akteure sprechen, die diese Technologien nutzen, und darüber, wie das alles abläuft.
Die Kombination von Bitcoin und Psychedelika
Während jede dieser Technologien für sich genommen lebensverändernd sein kann, eröffnet ihre Kombination einzigartige Möglichkeiten für den Einzelnen und die Menschheit als Ganzes. Bitcoin und Psychedelika sind wie Musikinstrumente, die jeweils mit ihrer eigenen, einzigartigen Frequenz schwingen. Jedes Instrument kann für sich allein ein Lied spielen, aber zusammen vervielfachen sich die symphonischen Möglichkeiten exponentiell. Wenn sie zusammen gespielt werden, schwingen die Frequenzen der Instrumente nahtlos mit und verwandeln sich für immer in tiefere, reichere Lieder.
In meinem eigenen Leben schreibe ich den Psychedelika einen direkten Einfluss auf die Kunst zu, die ich mache. Ohne Psychedelika hätte ich vielleicht Kunst in irgendeiner Form geschaffen, aber sie sähe nicht so aus und wäre nicht von denselben Designentscheidungen und Motivationen geprägt. Mein gesamtes Kunstportfolio ist ein direktes und eindeutiges Ergebnis der intensiven persönlichen Beschäftigung mit revolutionären psychedelischen Technologien wie LSD und Bitcoin. Ich habe Bitcoin durch eine Kombination aus Kunst, Psychedelika und natürlich Bitcoin kennengelernt. Früher habe ich LSD Blotter Art Designs gemacht, Kunst, die in winzige Quadrate perforiert und dann von den Chemikern mit LSD getränkt wurde. Ich habe auch das LSD-Mandala entworfen, das die soziale Geschichte, die Chemie und die Geheimnisse der LSD-Verteilung in einem grafischen Kodex verschlüsselt.
Ein anonymer Bitcoiner aus Brasilien fragte mich 2015, ob ich Bitcoin für meine Kunst nehmen würde, da es für ihn der einfachste Weg sei, internationale Transaktionen durchzuführen. Ich hatte zwar von Bitcoin gehört, wusste aber nicht, wie ich sie annehmen sollte. Ich sagte ihm: „Klar, aber du musst mir sagen, wie ich das einrichten soll". Dieser anonyme Fremde half mir, meine erste Bitcoin-Brieftasche einzurichten, schickte mir 3,1 Bitcoin für meine Kunst und verschwand dann prompt wieder im Internet, ohne dass ich je wieder von ihm gehört hätte. Ich vergaß Bitcoin, aber ein paar weitere „Berührungspunkte" mit Bitcoin im Laufe der Jahre waren wie eine Reihe von Neonpfeilen, die auf eine wichtige Botschaft des Universums hinwiesen.
Im Dezember 2017 machte ich meine erste Bitcoin-Kunst. Dieser Themenwechsel war für mich sehr wichtig, da ich meine Kunst als eine Methode betrachte, meine Botschaft in die Welt zu tragen. Wenn ich mich auf etwas einlasse, nimmt es mein ganzes Leben in Beschlag. Psychedelika waren über ein Jahrzehnt lang mein Thema gewesen, daher war dieser Wechsel für mich von großer Bedeutung.
Ich ließ mich schnell auf den Mist ein und glaubte etwa anderthalb Jahre lang lächerliche Dinge wie „Ethereum ist die Zukunft der Kunst" und andere ebenso zweifelhafte Dinge. Aber wie ich schon sagte, wenn ich mich für etwas interessiere, bin ich davon eingenommen. Ich untersuche es so gründlich, wie ich kann.
Ich fing an, NFTs zu untersuchen, lernte, wie sie kodiert sind und wie sie funktionieren, und je mehr ich lernte, desto desillusionierter wurde ich. Durch die Verwendung einer Reihe von Shitcoins in Kombination mit Psychedelika erkannte ich schnell, dass ich auf dem falschen Weg war. Ich konnte auch den richtigen Weg klar erkennen. Der eine Weg führt mich in die Dunkelheit und Zerstörung, zu Lügen und Betrug, der andere führt zu Wahrheit und Stabilität. Mein Weg ist Bitcoin, einzig und alleine. Ich kann mich nicht länger von den falschen Versprechungen und der Sackgasse in der Müllhalde der Shitcoinerei ablenken lassen.
Es gab eine harte Grenze, eine Schwelle, und ich habe sie im Juni 2019 überschritten. Während ich an einem Hackathon-Projekt für die Bitcoin-Konferenz 2019 arbeitete, machte ich eine psychedelische Erfahrung, die mir einen Strich durch die Rechnung machte. Während ich an einem (wirklich kitschigen) „Super-Bowl-Werbespot für Bitcoin" arbeitete, traf mich der Entschluss auf einmal; ich loggte mich in die Börse ein und tauschte alle meine Shitcoins gegen Bitcoin. Und meine Kunst sollte von nun an nur noch in Bitcoin gemacht werden.
Im folgenden Monat flog ich nach San Francisco zur Bitcoin 2019 Konferenz. An jenem Freitag während der Konferenz hörte ich, wie jemand die Uhr und den kalenderähnlichen Charakter von Bitcoin erwähnte. Ich nahm an diesem Abend LSD und ging zu einem Bitcoin-Entwicklertreffen, das nur wenige Blocks von meinem Hotel entfernt stattfand. Nachdem ich einen ganzen Tag und Abend LSD und Bitcoin-Inhalte konsumiert hatte, verbrachte ich die Nacht damit, die allerersten Konzeptentwürfe für die Bitcoin Full Node Skulptur zu skizzieren. In den nächsten sieben Monaten arbeitete ich unermüdlich, mied Freunde, Fernsehen, Twitter und Schlaf, um immer mehr zu schaffen.
Dabei verband ich Bitcoin und Psychedelika direkt mit dem Wunsch, ein Kunstwerk zu schaffen, das Bitcoin über Zeit, Raum, Geist und die Menschen, die das Netzwerk bilden, abbildet. Dieser Prozess erstreckte sich über die gesamten sieben Monate und ich habe in dieser Zeit LSD auf unterschiedliche Weise eingesetzt. Ich fand es in zwei Bereichen besonders hilfreich:
- Für ganzheitliches, übergreifendes Denken. Um die Visionen zu erhalten und festzuhalten, die ich von der Idee in die Form bringen wollte. Das sind in der Regel höhere Dosen, und ich arbeite während dieser Erfahrung nicht an der Kunst. Ich überdenke das Projekt in meinem Kopf und beobachte, wie es entsteht. Ich mache mir Notizen und mache einfache Skizzen, ohne Druck, halte alles fest.
- Für das Arbeiten in einem Flow-Zustand. Hier hast du direkten Zugang zum kreativen Fluss, während du an der Kunst arbeitest. Die Zeit löst sich auf, und alles fällt weg. Du und der kreative Prozess brennt im Einklang. In diesen Phasen kann eine fantastische Menge an Arbeit in kurzer Zeit erledigt werden.
Beides miteinander zu verbinden, bedeutet nicht immer, dass man beides zur gleichen Zeit braucht. Ich habe ein Sprichwort: „Erschaffe high, bearbeite nüchtern". Bringe deine Ideen, Fähigkeiten und Leidenschaften in die psychedelische Erfahrung ein und konzentriere all das auf eine bestimmte Mission, ein Ziel. Nutze diese rohe, ungeschliffene Inspiration und forme sie mit einem ruhigen Geist. Den Nutzen aus jedem dieser Zustände zu ziehen, war entscheidend für die Erstellung der Bitcoin Full Node Skulptur.
Während des Prozesses lernte ich viel über Bitcoin und seine Funktionsweise, indem ich versuchte, es visuell zu beschreiben. Man kann nicht beschreiben, was man nicht versteht. Ich habe auch viele Erkenntnisse gewonnen, indem ich verschiedene Aspekte von Bitcoin visualisiert habe. Ich konnte sehen, wie wichtige Teile auf neue Weise zusammenpassen, und mein Verständnis vertiefte sich durch die Fähigkeit, Konzepte geometrisch zu visualisieren.
Jede Reise besteht aus drei Teilen, die jeweils ein paar Stunden dauern. Der Aufschwung, der Höhepunkt und der Abschwung. Jede oder alle (oder keine) dieser Phasen kann für die Kreativität genutzt werden. Wenn die Intensität des Trips nachlässt, ist die Phase des Ausklingens für mich eine äußerst produktive Phase.
Ich erzähle dir von einer meiner Methoden, um LSD für deine Kreativität zu nutzen, wobei ich mir bewusst bin, dass das, was für mich funktioniert, für dich vielleicht nicht funktioniert. Die Methode ist sehr einfach. Sie setzt voraus, dass du gutes LSD in einer bekannten Dosierung auf dem Papier hast. (Und du weißt zuverlässig, wie stark eine Dosis auf dich wirkt).
- Schneide dein LSD je nach Potenz in 3er oder 4er Stücke. Du willst, dass diese Menge ausreicht, um etwas zu spüren. Es sollte keine Dosis unterhalb der Wahrnehmungsschwelle sein.
- Beginne damit, ein Viertel einer Standarddosis zu nehmen. Manchmal reicht das schon aus, dann kannst du hier aufhören.
- Nachdem du 60 Minuten gewartet hast, nimmst du eine weitere Vierteldosis. Du kannst weiterhin jede Stunde eine viertel Dosis einnehmen. Ich habe keine feste Grenze dafür gefunden, wie lange das so weitergehen kann.
- Konzentriere dich bei dieser Erfahrung auf ein bestimmtes Projekt oder Problem.
- Lege eine Zeit und einen Ort fest, an dem du nicht gestört oder abgelenkt wirst.
- Halte alle Werkzeuge bereit, die du brauchst.
Indem du die Dosis über die Zeit verteilst, vermeidest du die Intensität einer krachenden LSD-Welle, die dich auf einmal trifft. Indem du die Dosis verteilst, wird es einfacher, in den psychedelischen Raum zu gelangen und sich darin zurechtzufinden. Es gibt weniger Rucke zwischen dem normalen Wachbewusstsein und der LSD-Gedankenwelt, weil das eine leicht in das andere überzugehen scheint. Außerdem wird die Intensität des Erlebnisses insgesamt abgeschwächt, während es gleichzeitig verlängert wird und leichter zu bewältigen ist.
Auf einer tieferen Ebene werden Psychedelika und Informatik schon seit Jahrzehnten kombiniert, und ich habe viele faszinierende Beispiele gefunden, wie Menschen dies erfolgreich tun.
Ein Computerprogrammierer auf Reddit scheint eine ähnliche Technik zu verwenden, wie ich sie oben beschrieben habe.
„Du kannst auch versuchen zu programmieren, während du auf einer leichteren Dosis bist. Das kann eine ziemlich erstaunliche Erfahrung sein, denn du kannst mit einem Bruchteil eines Tabs trippen und programmieren. Wenn du das machst, nimm dir ein Problem vor, mit dem du anfängst, bevor du trippst, aber hab keine Angst davor, den Gang komplett zu wechseln und etwas völlig anderes, verrücktes und wunderbares zu machen." -u/tosler
\ Wenn du ein Psychedelikum nimmst und über ein Thema nachdenkst, auf das du neugierig bist, kann das zu neuen und neuartigen Ideen und Lösungen führen. Als z. B. der Nobelpreisträger Kary Mullis die PCR erfand, schrieb er die Nobelpreis-Idee direkt seinen Erfahrungen mit LSD zu.
„Hätte ich die PCR erfunden, wenn ich kein LSD genommen hätte? Das bezweifle ich ernsthaft... Ich könnte auf einem DNA-Molekül sitzen und den Polymeren zusehen, wie sie vorbeiziehen. Das habe ich zum Teil auf psychedelischen Drogen gelernt." - Kary Mullis

\ Ein weiteres hervorragendes Beispiel für eine wissenschaftliche Studie über die kreativitätsfördernden Eigenschaften der Kombination von psychedelischen Drogen mit bestimmten Interessens- oder Forschungsgebieten stammt aus einer Studie, die vor der Illegalisierung von LSD durchgeführt wurde. Das ist deshalb wichtig, weil LSD in der Öffentlichkeit noch nicht mit dem negativen Stigma der „Illegalität" oder „Unmoral" behaftet war, da es keine Gesetze gegen den Konsum von LSD gab.
An der Studie nahmen 27 Personen teil, „darunter Ingenieure, Physiker, Mathematiker, Architekten, ein Möbeldesigner und ein Werbegrafiker. Die Probanden wurden angewiesen, ein oder mehrere Probleme auszuwählen, die eine kreative Lösung erforderten und an denen sie wochen- oder monatelang gearbeitet hatten, ohne eine zufriedenstellende Lösung finden zu können."
Und jetzt kommt der Clou: Noch Monate nachdem die Wirkung nachgelassen hatte, blieben die Teilnehmer standhaft: LSD hatte ihnen absolut geholfen, ihre komplexen, scheinbar unlösbaren Probleme zu lösen. Und die Einrichtung stimmte zu.
Kurz nach ihren LSD-Erfahrungen brachten die 27 Männer eine Reihe von Innovationen auf den Weg, die weithin Anerkennung fanden, darunter:
- ein mathematisches Theorem für NOR-Gatter-Schaltungen
- ein konzeptionelles Modell für ein Photon
- eine Vorrichtung zur Strahlsteuerung eines linearen Elektronenbeschleunigers
- ein neues Design für das Vibrationsmikrotom
- eine technische Verbesserung des Magnetbandrekorders
- Entwürfe für eine private Residenz und einen Kunsthandwerker-Einkaufsplatz
- ein Experiment für eine Raumsonde zur Messung der Sonneneigenschaften
Da LSD illegal ist, werden wir vielleicht nie erfahren, wie viele Entdeckungen und Erfindungen das direkte Ergebnis der Kombination von Psychedelika mit der Leidenschaft und den Fähigkeiten eines Menschen sind. Viele Berufstätige hatten und haben immer noch zu viel Angst vor beruflichen oder gesellschaftlichen Konsequenzen aufgrund ihres Konsums von Psychedelika. Glücklicherweise schweigen nicht alle zu diesem Thema. Dennis Wier, ein Computerprogrammierer, hat diese Geschichte erzählt:
"So habe ich 1975 LSD-25 für ein komplexes Programmierprojekt verwendet. Ich arbeitete in New York an der Entwicklung eines Compilers für eine Anwendungssprache namens "MARLAN". An einem bestimmten Punkt des Projekts konnte ich keinen Überblick über die Funktionsweise des gesamten Systems gewinnen. Es war wirklich zu viel für mein Gehirn, all die subtilen Aspekte und Verarbeitungsnuancen im Blick zu behalten, um einen Überblick über die Verarbeitung und das Design zu bekommen. Nachdem ich einige Wochen lang mit diesem Problem gekämpft hatte, beschloss ich, ein wenig Säure zu verwenden, um zu sehen, ob dies einen Durchbruch bringen würde.\ \ Ich nahm nur fünfundsiebzig Mikrogramm, weil ich kein Interesse daran hatte, zu trippen, denn ich hatte ein bestimmtes, begrenztes und eindeutiges Ziel für den Gebrauch von LSD. Während ich durch das LSD stimuliert wurde, konnte ich mir das gesamte System gleichzeitig vor Augen führen. Ich verbrachte einige Zeit damit, mir verschiedene Aspekte des Compilers, der Sprache und der Verarbeitung vor Augen zu führen. Unter dem Einfluss von LSD entdeckte ich drei oder vier Ungereimtheiten im Design und machte mir Notizen, um sie später zu überprüfen.\ \ Nachdem alle Änderungen vorgenommen worden waren, konnte ich die Programmierung dieses riesigen Systems erfolgreich abschließen. Die von mir vorgenommenen Änderungen verringerten künftige Fehler bei der Programmänderung und trugen zur Eleganz des Entwurfs bei. Das System war ein kommerzieller Erfolg für meinen Arbeitgeber und wurde von ihm viele Jahre lang genutzt. Obwohl die Verwendung von LSD eine wichtige Komponente für den Erfolg des Systems war, wusste außer mir niemand von seiner Verwendung."
\ Bill Atkinson, der Erfinder von HyperCard, gab zum ersten Mal öffentlich bekannt, dass die gesamte Idee für seine Softwareerfindung auf einem LSD-Trip entstand, den er bei 1:03:45 in diesem Video anschaulich beschreibt.
„Ich will nicht behaupten, dass jeder Softwareentwickler auf der Welt LSD nehmen sollte, aber bei mir hat es funktioniert." -Bill Atkinson
\ 1987 revolutionierte Apple die Art und Weise, wie Menschen mit ihren Computern interagieren, indem es HyperCard kostenlos zu jedem verkauften PC lieferte. Das Programm wurde dafür gelobt, „die Möglichkeiten der Computerprogrammierung und des Datenbankdesigns in die Hände von Nicht-Programmierern zu legen". Es wurde zu einem der ersten Werkzeuge für das elektronische Publizieren. HyperCard selbst war ein Werkzeug zur Selbstbestimmung, das von einem Programmierer entwickelt wurde, der zwei andere Werkzeuge zur Selbstbestimmung nutzte. Das ist eine sehr interessante Situation, in der die Werkzeuge neue Werkzeuge hervorbringen, die von den Menschen, die sie benutzen, hergestellt werden, und die neuen Werkzeuge sind auf dasselbe Ziel ausgerichtet wie die ursprünglichen Werkzeuge - die Erhöhung der Selbstsouveränität.
Ich möchte ein letztes Beispiel für einen Computerprogrammierer anführen, der LSD und dezentrale Netzwerke für sein Streben nach Selbstbestimmung nutzte. Kevin Paul Herbert, ein autodidaktischer Computerprogrammierer und Softwaredesigner, der Software entwickelt hat, die heute auf Millionen von Internet-Routern weltweit läuft, gab 2008 dieses Interview.
"Psychedelika sind besonders hilfreich bei der Entwicklung neuer Computertechnologien. Sie müssen etwas an der internen Kommunikation in meinem Gehirn verändern. Was auch immer mein innerer Prozess ist, der mich Probleme lösen lässt, er funktioniert anders, oder vielleicht werden andere Teile meines Gehirns benutzt. Wenn ich auf LSD bin und etwas höre, das reiner Rhythmus ist, versetzt mich das in eine andere Welt und in einen anderen Gehirnzustand, in dem ich aufgehört habe zu denken und angefangen habe zu wissen." - Kevin Paul Herbert
\ Ein letztes Zitat von Kevin Herbert geht wirklich auf die tiefgreifenden Fragen ein, die den selbstbestimmten Technologien zugrunde liegen. Vergiss nicht, dass er über all das bereits 2008 nachgedacht hat.
"Was steht für unsere Freiheit? Was steht dafür, was die Regierung regulieren darf und aus welchem Grund?
Wohin uns das führt, hängt davon ab, ob wir bereit sind, ein Modell zu akzeptieren, in dem die Dinge offen sind - einschließlich unseres eigenen Verstandes - oder ein Modell, in dem die Dinge geschlossen sind - einschließlich unseres eigenen Verstandes und der Dinge, über die wir nachdenken können, sowie der Chemikalien, die wir einsetzen können, um unser Denken zu beeinflussen." - Kevin Paul Herbert
\ Sei dir bewusst, dass diese Erfahrungen durch den Lebensweg des Einzelnen geprägt sind. Je mehr du weißt und je mehr Fähigkeiten du hast, desto mehr werden sie den Inhalt deiner psychedelischen Erfahrungen beeinflussen. Was auch immer dein Interesse, deine Leidenschaft oder dein Handwerk ist, wenn du diese Technologien nutzt, um deine Kreationen zu beeinflussen, werden sie sich zweifellos verändern und weiterentwickeln. Auf welche Weise, kann ich nicht sagen - das liegt an dir.
Ich glaube, wir alle sind in der Lage, Meisterwerke zu schaffen. Ein Automechaniker kann so gut sein, dass man ihn für einen Künstler hält. Das Gleiche gilt für einen Koch, einen Anwalt oder einen Lehrer - alle diese Berufe können bis zu einem gewissen Grad meisterhaft ausgeübt werden. Finde deine Leidenschaft, folge ihr und schaffe deine Meisterwerke.
Ich glaube, dass wir mit diesen Werkzeugen der Selbstbestimmung als Individuen wachsen können und die Möglichkeit haben, die Welt um uns herum auf tiefgreifende Weise zu beeinflussen.
Ursprungsgeschichten
\ Ein mysteriöser Cypherpunk hat an Halloween 2008 anonym ein White Paper in einem obskuren Kryptografieforum veröffentlicht. Er oder sie bleibt lange genug dabei, um das revolutionärste Geldsystem der Welt in seinen Kinderschuhen zu halten, und verschwindet dann wieder. Es wird viel darüber diskutiert, ob Satoshi eine Person oder viele ist, männlich oder weiblich, lebendig oder tot. Alles ist von Geheimnissen umhüllt.
Auch die Ursprünge der Psychedelika sind umstritten. Terence McKenna verbreitete die „Stoned-Ape-Theorie", nach der sich gedankenlose Affen durch den Konsum von psychedelischen Pilzen auf dem afrikanischen Kontinent zu Menschen entwickelten. Ob das stimmt oder nicht, die Ursprünge dieser Beziehung gehen zweifellos auf eine Zeit vor der aufgezeichneten Geschichte zurück.
Noch mysteriöser ist die Entstehungsgeschichte von LSD. Die berühmte „Bicycle Day"-Geschichte ist höchstwahrscheinlich eine Erfindung. Eine gründliche Untersuchung der Behauptungen in dieser Geschichte führt zwangsläufig zu dem Schluss, dass die Dinge unmöglich zusammenpassen. Wir sollen glauben, dass eine Kaskade von „Unfällen" zu der unerwarteten Entdeckung der stärksten Substanz geführt hat, die der Menschheit bekannt ist.
Vertraue nicht, überprüfe. Ohne dich zu weit in dieses Kaninchenloch zu führen, stelle ich dir diese Präsentation des LSD-Chemikers Dave Nichols von der Mind States-Konferenz 2004 zur Verfügung, und du kannst hier anfangen zu deine eigenen Nachforschungen azustellen (DYOR). Dr. Nichols ist in seinen Schlussfolgerungen weitaus freundlicher als ich, und ich habe einen separaten Artikel, in dem ich die wahre Geschichte hinter dem Bicycle Day noch viel ausführlicher darstelle. Die Ursprünge von LSD und Bitcoin sind auf ähnliche Weise von Geheimnissen und Legenden umwoben.
Es gibt drei unterschiedliche Versionen in der Entstehungsgeschichte von Bitcoin und LSD:
- Was tatsächlich geschah
- Was uns erzählt wird
- Vollständige Erfindungen und Fehlinformationen über das, was passiert ist
Wie auch immer sie ursprünglich entstanden sind, die unumstößliche Tatsache ihrer Existenz zwingt uns heute dazu, uns damit auseinanderzusetzen, was diese Technologien für jeden Einzelnen von uns und für das weltweite Kollektiv bedeuten.
Der Schöpfer und die Geheimdienste
\ Auch wenn sie umstritten sind, gibt es angebliche Verbindungen zwischen Satoshi Nakamoto und Albert Hoffman, den Schöpfern von Bitcoin und LSD, und Geheimdiensten mit drei Buchstaben wie der CIA und der NSA. Bei Satoshi gibt es sowohl Behauptungen, dass er wegen der CIA in die Bitcoin-Gemeinschaft kam, als auch, dass er sie verließ. Bekanntlich verschwand er ein für alle Mal, als der Bitcoin-Entwickler Gavin Andreson beschloss, sich mit der CIA zu treffen, um sie über Bitcoin aufzuklären. Die NSA hat den SHA-256-Algorithmus entwickelt, der in Bitcoin verwendet wird, was zu weiteren Satoshi-Verschwörungstheorien führt.
Es gibt auch Behauptungen, dass Albert Hofmann, der Erfinder von LSD, ein Mitarbeiter der CIA war oder wurde und mit dem St. Anthony Brand in Port Saint Esprit, Frankreich, im Jahr 1951 in Verbindung gebracht wurde. Es gibt noch viele weitere Behauptungen über Verbindungen der Geheimdienste zu den Erfindern von LSD und Bitcoin, die mehr oder weniger glaubwürdig sind. Diese Behauptungen sind zwar unterhaltsam, können aber in den meisten Fällen weder bewiesen noch widerlegt werden, so dass uns eine rationale Untersuchung nur bedingt weiterbringt.
Die frühe Revolution durch Computer
\ Eine unbestreitbare Verbindung zieht sich durch die einzelnen Revolutionen des Computers, der Psychedelika, der Kryptografie und des Bitcoin. Sie alle sind in einem komplexen Geflecht der Selbstverwirklichung miteinander verbunden. Es ist erstaunlich, dass die frühe Computer-, die öffentliche Kryptografie- und die psychedelische Revolution alle auf denselben Ort und dieselbe Zeit zurückgehen.
Die Zeit von Anfang der 1950er Jahre bis 1965 wurde in der San Francisco Bay Area in Kalifornien zu einem Sammelbecken für selbstgebaute Computer, Mathematiker und LSD. In der Zeit von 1966 bis 1976 wurden sowohl LSD als auch der Personal Computer zu Werkzeugen der Revolution und des persönlichen Wachstums. Um den Verbindungen zwischen LSD und Bitcoin auf die Spur zu kommen, müssen wir in diese Zeit zurückgehen und die Fäden zurückverfolgen, die einen Wandteppich der Transformation durch diese beiden Gemeinschaften webten und sie für immer verbanden.
Da LSD in Kalifornien erst 1966 verboten wurde, gab es einen Zeitraum von über einem Jahrzehnt, in dem Informatik und psychedelische Wissenschaft in akademischen Kreisen nebeneinander existierten.
Zwischen 1950 und Mitte der 1960er Jahre wurden mehr als tausend klinische Abhandlungen, mehrere Dutzend Bücher und sechs internationale Konferenzen über die Therapie mit psychedelischen Drogen veröffentlicht. Diese Geschichte aus dieser Zeit verbindet das frühe Informatikpublikum mit dem frühen Gebrauch von LSD in der Bay Area:
„Von 1961 bis 1965 führte die in der Bay Area ansässige International Foundation for Advanced Study mehr als 350 Menschen zu Forschungszwecken auf LSD-Trips. Einige von ihnen waren wichtige Pioniere in der Entwicklung der Computertechnik, wie z.B. Doug Engelbart, der Vater der Computermaus."
LSD wurde in vielen führenden Computerfirmen der 1950er und 60er Jahre eingesetzt, vom Systemdesign bis hin zum Entwurf von Computerschaltkreisen:
„Einige der frühen Computeringenieure verließen sich beim Entwurf von Schaltkreisen auf LSD, vor allem in den Jahren, bevor sie auf Computern entworfen werden konnten, denn „man musste in der Lage sein, sich eine schwindelerregende Komplexität in drei Dimensionen vorzustellen und alles im Kopf zu behalten. Und sie fanden heraus, dass LSD dabei helfen konnte."
Timothy Leary, Harvard-Professor und bekannter Psychedeliker, wurde zu einem ausgesprochenen Befürworter der Macht des Computers als Werkzeug für persönliches Wachstum. Er sah den PC als eine Technologie an, die den Geist auf ähnliche Weise öffnen kann wie das LSD.
„Der PC ist das LSD der 1990er Jahre". -Timothy Leary
LSD war im Silicon Valley der 1960er Jahre allgegenwärtig. Informatiker, Programmierer und Designer aller großen Unternehmen waren daran beteiligt. Diese Geschichte aus dem Wired Magazine geht auf die Verbindungen zwischen Psychedelika, dem Internet und den Grateful Dead ein. Auch wenn diese Geschichte 25 Jahre vor der Geburt von Bitcoin spielt, klingt der folgende Absatz sehr nach Bitcoin:
„Ein Teil der Magie dieser Transaktion besteht darin, dass es gelungen ist, nützliche Inhalte über Jahrzehnte hinweg über das Netzwerk zu teilen. Aber eine andere, noch erstaunlichere Tatsache ist die Widerstandsfähigkeit der Daten, die von Maschine zu Maschine mit einer Art Lebenskraft weitergegeben wurden. Irgendetwas in ihnen machte sie selbstreplizierend und lebendig, etwas, das darum bettelte, kopiert und geteilt, angehört und gesungen zu werden."
Wir können sehen, dass die Anfänge der Computer- und der psychedelischen Revolutionen beide auf diesen konzentrierten Knotenpunkt von Ort und Zeit zurückgehen. Diese Flüsse scheinen in dieselben Meere zu fließen und denselben Quellen zu entspringen. Es gibt Überschneidungen zwischen den scheinbar getrennten Subkulturen, die sich in den frühen Computer- und Psychedelik-Gemeinschaften gebildet haben. Viele Denker, Autoren, Wissenschaftler und Forscher der damaligen Zeit kamen durch soziale Umstände oder durch ihre Berufe in engen Kontakt.
Der Weg von der Entwicklung von Kontrollinstrumenten für Unternehmen hin zur Entwicklung von Instrumenten für Menschen, die sich der Kontrolle widersetzen, hat sich über Jahrzehnte vollzogen.
\ Wir alle sind Nutznießer der Arbeit psychedelischer Informatikerinnen und Informatiker aus einer nicht allzu fernen Vergangenheit.
Wir haben diese klare Verbindung zwischen der psychedelischen und der Computer-Revolution gesehen und können nun auch die öffentliche Kryptografie-Revolution direkt mit beiden in Verbindung bringen. Die Kryptografie war ein streng gehütetes Geheimnis der staatlichen Geheimdienste, bis Whitfield Diffie und Martin Hellman das geheime Wissen aus der Versenkung holten und es dem Normalbürger zugänglich machten.
Diese Frechheit blieb nicht ohne Folgen. Die Regierung versuchte, die Verschlüsselung zu verbieten, indem sie sie als Kriegsmunition einstufte und das Schreiben und Veröffentlichen von kryptografischem Code illegal machte. Die Verwendung von Kryptografie wäre das Gleiche wie ein Waffenhändler zu sein. Dies führte zu den Verschlüsselungskriegen in den 1980er und 1990er Jahren.
Auch hier befinden wir uns wieder in dieser punktgenauen Verknüpfung von Zeit und Ort. Der Held unserer Geschichte tritt in die Schlacht ein und verändert den Lauf der Menschheitsgeschichte für immer. 1965, nachdem er das MIT verlassen hatte, bekam Whit Diffie dank seiner Kenntnisse über Psychedelika einen Job und reiste 1969 (du hast es erraten) in die San Francisco Bay Area.
1975 veröffentlichte er seine Arbeit zur Public-Private-Key-Kryptografie, die die Grundlage für das gesamte Bitcoin-System bildet.
\ John Markoff beschreibt diese psychedelische Verbindung in seinem Buch „What the Dormouse Said: How the Sixties Counterculture Shaped the Personal Computer Industry":
"Diffies Bewerbungsgespräch bei der MITRE Corporation fand mit einem angesehenen Mathematiker und Softwareentwickler namens Roland Silver statt, der sein Mentor wurde. Es war ein ungewöhnliches Vorstellungsgespräch, wenn man bedenkt, dass es sich um einen Militärdienstleister handelte. Es fand in Silvers Haus statt, und fast das gesamte Gespräch drehte sich um psychedelische Drogen: wie man sie zubereitet, wo man sie bekommt usw. Diffie hat mit Bravour bestanden."
Diffie war auch ein großer Verfechter der persönlichen Freiheit und Selbstbestimmung. Als er erfuhr, dass die Geheimdienste der Regierung Wissen über kryptografische Mathematik versteckten, wird er mit den Worten zitiert
"Kryptografie ist für die menschliche Privatsphäre unerlässlich! Vielleicht sollten leidenschaftliche Forscher/innen im öffentlichen Sektor versuchen, das Thema zu befreien. Wenn wir uns anstrengen, könnten wir eine Menge von diesem Material wiederentdecken."- Whitfield Diffie
Nachdem Whitfield und Hellmann ihre bahnbrechende Arbeit über die Kryptografie mit öffentlich-privaten Schlüsseln veröffentlicht hatten, fragte ein anderer Forscher aus der Bay Area an, ob sie an einer Zusammenarbeit interessiert seien. Es handelte sich um Ralph Merkle, den Erfinder einer weiteren wichtigen Technologie, die Bitcoin zugrunde liegt: des Merkle-Baums.
Während eines sehr kurzen Moments in der Geschichte leuchtet dieses sehr kleine geografische Gebiet wie ein magisches Ei, das Technologien des Wandels und der Hoffnung hervorgebracht hat.
\ Die tief verwobenen Verbindungen zwischen der Entstehung der Revolutionen der Psychedelika, des Personal Computing und der Kryptografie sind wirklich bemerkenswert. Diese drei Wissenschaften konvergieren in den nächsten Jahrzehnten in Ausdrucksformen der Selbstsouveränität durch digitale Privatsphäre, digitales Geld und digitale Philosophie, die durch „Cypherpunks, die Code schreiben" verwirklicht werden.
Bevor wir uns den historischen Verbindungen zuwenden, wäre ich nachlässig, wenn ich nicht Ross Ulbricht und Silk Road erwähnen würde. Einer der sichtbarsten Aspekte der frühen Bitcoin-Geschichte war die Beziehung zwischen Online-Peer-to-Peer-Marktplätzen, Bitcoin und Psychedelika. Im Jahr 2011 wurde die Welt mit einer neuen Art von „Drogenmarkt" konfrontiert. Dieser neue Online-Marktplatz bot sowohl den Käufern als auch den Verkäufern einzigartige Vorteile.
Viele wissen es nicht, aber Ross baute seine eigenen psychedelischen Pilze an, die das allererste Produkt auf der Silk Road-Website sein sollten. Bevor es etwas anderes gab, gab es Bitcoin und Psilocybe cubensis. Abgesehen von Lazlo's Pizza sind psychedelische Pilze also wohl einer der ersten aufgezeichneten Peer-to-Peer-Tauschgeschäfte von Bitcoin gegen Waren/Dienstleistungen. Auch wenn es einige Papierhandtücher, Tassen und andere banale und vergessene Gegenstände gibt, ist die Verbindung zwischen der Online/P2P/Psychedelic/Cypherpunk-Community unbestreitbar.
Interessanterweise war der erste Ort, an dem Ross für die Silk Road warb, das psychedelische Pilz-Online-Forum The Shroomery, unter dem Benutzernamen "altoid". Du kannst seinen einzigen Beitrag hier nachlesen.
Die Ebene der Umsetzung
\ Die nächste Ebene, auf der man nach interessanten Parallelen suchen kann, ist die einfachste Ebene der Grundlagen der einzelnen Implementierungen. Bitcoin ist ein Protokoll, ein Satz von Regeln, Anweisungen und Parametern, und es gibt verschiedene Implementierungen von Bitcoin, die mit dem Protokoll kompatibel sind. Die Implementierungen sind die Software, die du ausführst und die es dir ermöglicht, mit dem Netzwerk zu interagieren. Obwohl es eine Standard-„Referenzimplementierung" von Bitcoin gibt, haben die Nutzer die völlige Freiheit, verschiedene Programmiersprachen, Funktionen und Architekturen zu verwenden, um mit demselben Bitcoin-Netzwerk zu interagieren wie alle anderen.
Die meisten Bitcoin-Nutzer schätzen zwar die Möglichkeit, dies zu tun, aber werden wir werden eigene Bitcoin-Implementierung nicht von Grund auf programmieren. Wir werden aus den vielen verfügbaren Implementierungen wählen und entscheiden, ob wir Open-Source- oder Closed-Source-Code verwenden.
Dieses Thema ist zu umfangreich für diesen Artikel, aber ich bin der festen Überzeugung, dass man Bitcoin niemals mit Closed-Source-Code verwenden sollte. Wenn du dich für Open-Source-Code entscheidest, kannst du die Software anhand ihres Quellcodes sowohl überprüfen als auch kompilieren.
Hier gibt es eine Menge Nuancen. Auf dieser Ebene können die „Werkzeuge" von Bitcoin so austauschbar sein wie das Auto, das du fährst, und der Endnutzer hat fast die gleiche Auswahl. Diese Wahl ist wichtig und sollte gut überlegt sein. Das Auto, das du fährst, ist vielleicht an den meisten Tagen unbedeutend, aber eines Tages könnte es aufgrund bestimmter Eigenschaften deine Familie retten.
Wichtig ist, dass unabhängig von der Implementierung, für die sich ein Nutzer entscheidet, die Möglichkeit, seinen eigenen Knotenpunkt zu betreiben, der demokratisierende und wohl auch wichtigste Faktor ist. Jeder sollte in der Lage sein, seinen eigenen Knotenpunkt zu betreiben und dabei Zwischenhändler und Unsicherheiten auszuschalten.
Ein Bitcoin-Knoten ist eine Quelle der Wahrheit - eine vollständige Geschichte von der Gegenwart bis zurück zur Genesis. Indem du deinen eigenen Knotenpunkt betreibst, erhältst du deine eigene direkte Quelle der Wahrheit, die nicht von Banken, Politikern oder Priestern vermittelt wird. Für Bitcoin bedeutet dies, dass die Nutzer mit Sicherheit wissen können, dass ihre eigenen Transaktionen gültig und echt sind - ohne einen Goldbarren einschmelzen zu müssen, um das zu überprüfen, was teure Ausrüstung und Zeit kostet. Wenn der Bitcoin in meiner Wallet ankommt, weiß ich, dass er zu 100% echt ist. Er ist nicht gefälscht und nicht entwertet. Es ist reiner, unverfälschter Bitcoin.
Bei psychedelischen Drogen kannst du sie selbst anbauen, synthetisieren und/oder extrahieren, ohne dass du Zwischenhändler brauchst oder dir Sorgen über Reinheit, Gewicht oder falsche Identifizierung machen musst.
Psychedelika ermöglichen es dir, wie Sama Katharo es formulierte: „dich mit deinem eigenen inneren Knotenpunkt zu verbinden". Die Software der komplexesten und am dichtesten verzweigten Verarbeitungsmaschine, die der Mensch kennt: dein Gehirn. Du kannst sie nutzen, um deine eigene Quelle der inneren Wahrheit zu destillieren. Du kannst die riesigen Gedankenwelten in deinem Kopf erforschen, ohne dass sich ein Psychiater oder eine andere „vertrauenswürdige dritte Partei" einmischen oder ihren Bezugsrahmen auf dich projizieren muss. Psychedelika geben dir die Schlüssel zu deinem eigenen inneren Palast.
Psychedelika gibt es, genau wie Bitcoin, in vielen verschiedenen Varianten, z. B. LSD, MDMA, Psilocybin, DMT, Meskalin oder Cannabis. Es gab auch einen Boom von experimentellen psychedelischen „Forschungschemikalien", die sich über die Darknet-Märkte (und damit auch über Bitcoin) verbreitet haben. Und obwohl der Betrieb eines großen psychedelischen Labors außerhalb der Möglichkeiten und Wünsche der meisten Menschen liegt, können fast alle Erwachsenen die Kontrolle über ihren psychedelischen Weg übernehmen und ihre eigenen Pilze, Kakteen und Cannabis anbauen. Dies kann in verschiedenen Ländern unterschiedliche rechtliche Konsequenzen haben, und jeder Nutzer muss entsprechend entscheiden.
Der Weg zum eigenen Anbau von psychedelischen Drogen ist eine heroische Suche nach Selbsterkenntnis, Vorbereitung, Wachstum und Geduld. Sich die Zeit zu nehmen, um die richtigen Materialien zu verstehen, zu kultivieren, zu pflegen und hervorzubringen, hat unermessliche Vorteile. Diese Vorbereitung und Kontemplation gibt dem Suchenden die Kontrolle darüber, was in unserem Körper passiert.
Auf dem Weg des Bitcoiners, der versucht, seine Zukunft in der Schuldenspirale zu kontrollieren, die sich um uns herum abspielt, gibt es eine ähnliche Heldentat.
Learning by Doing
\ Sowohl bei Bitcoin als auch bei Psychedelika ist es wichtig, dass du sie tatsächlich BENUTZEN kannst, bevor du sie richtig verstehen kannst. Du kannst ein Buch darüber lesen, wie sie funktionieren, was sie bewirken und wie man sie richtig einsetzt, aber dein Verständnis ist unvollständig, solange du sie nicht persönlich erlebt hast. Keine noch so gute Vorbereitung oder Lektüre kann dich auf den weltbewegenden Wirbelsturm vorbereiten, der das Herzstück der psychedelischen Erfahrung ist. Keine noch so gute Lektüre kann dich auf das Gefühl vorbereiten, das du bekommst, wenn du Bitcoin verschickst - eine kostspielige und unumkehrbare Aktion.
Je mehr du sie benutzt, desto besser wirst du mit ihnen vertraut. Je vertrauter du wirst, desto tiefer kannst du in die Erfahrung eintauchen. Das ist Weisheit, die aus Erfahrung entsteht, nicht Wissen, das man durch Lesen erlangt.
"Ein tiefes Verständnis von Bitcoin zu erlangen, ist wie ein tiefer psychedelischer Trip. Denn alles scheint sich um dieses Ideal herum auf unerwartete und ziemlich radikale Weise zu verändern, weil du die Dinge jetzt auf eine ganz andere Art und Weise siehst, als du sie ursprünglich zu sehen glaubtest." - Eric Cason
Endgültigkeit
\ Sowohl bei Psychedelika als auch bei Bitcoin gibt es einen Punkt an dem es keine Rückkehr mehr gibt. Wenn du eine Bitcoin-Transaktion abschickst, kannst du sie nicht mehr zurücknehmen. Sobald du auf „Senden" klickst und das Netzwerk die Transaktion bestätigt, kann keine deiner Handlungen mehr verhindern, dass der Bitcoin sich einmal bewegt. Wenn du dir einen Schuss LSD auf die Zunge legst oder ein paar Gramm Pilze isst, bist du für die nächsten Stunden an diese Erfahrung gebunden. Es gibt kein STRG+Z, keine Wiederholung oder Rückerstattung. Es gibt keinen Ausweg außer dem Durchgang.
Es gibt eine Schwelle, nach deren Überschreiten nichts mehr so ist, wie es einmal war. Diese Endgültigkeit gibt dem Benutzer eine Pause, um seine Handlungen zu überdenken. Ein Fehler oder Fehltritt hat hier unmittelbare Konsequenzen, daher ist es klug und umsichtig, vorsichtig vorzugehen. Es ist von größter Bedeutung, dass du deine Entscheidungen bei der Nutzung dieser Technologien sorgfältig triffst. Mit der Übung kommt die Vertrautheit. Und mit der Vertrautheit kommt das Vertrauen. Diese Technologien fördern bewusstes Handeln und führen zu Überzeugung, wenn sie mit Sorgfalt und Respekt eingesetzt werden.
Die Erlebnisse
\ Die Erfahrungen mit Psychedelika und Bitcoin bringen uns zu denselben grundlegenden Fragen über das Menschsein und die Interaktion mit dem Universum um uns herum.
- Was ist Zeit?
- Was ist Geld?
- Was ist real?
- Was ist Sprache?
- Was ist Arbeit?
- Was ist Energie?
- Ist der Einsatz von Energie gut oder schlecht?
- Wo gehöre ich zu meinen Mitmenschen?
Warum bringen uns diese beiden unterschiedlichen Technologien zu denselben grundlegenden Fragen über die Realität und das Menschsein? Warum inspirieren sie uns dazu, die großen Fragen zu stellen?
Das Konzept der Zeit ist auf mehreren Ebenen tief mit Bitcoin und Psychedelika verwoben. Bitcoin hat die Zeitmessung neu definiert, und die Folgen davon müssen erst noch verstanden werden. Die menschliche Erfahrung von Zeit ist variabel. Wir interpretieren die Zeit durch eine Linse anderer Wahrnehmungen (wenn du Spaß hast, scheint die Zeit schnell zu vergehen, während es dir, wenn du verzweifelt auf etwas wartest, vorkommen kann, als sei jede Sekunde eine Ewigkeit).
Dies wird durch Psychedelika noch verstärkt, da das Konzept der Zeit dehnbar und amorph wird und Neuartigkeit und Zufälligkeit mit der alltäglichen Erfahrung der Zeit wie ein Spiegelbild spielen. Vergleiche dies mit den Blockzeiten von Bitcoin. Blocks sollen alle 10 Minuten kommen, aber manchmal sind sie schneller, manchmal langsamer. Wie die Wellen im Ozean bewegt sich jeder Tick der Bitcoin-Uhr in seinem eigenen Rhythmus, ist aber endlos, wie die Zeit selbst.
Sowohl Bitcoin als auch Psychedelika haben ihren eigenen inneren Zeitrhythmus, der durch den Rhythmus der Uhr nicht beeinflusst oder verändert wird.
Integration: Unerfahrener vs. erfahrener Gebrauch
\ Bei Bitcoin und Psychedelika gibt es ein Spektrum an Vertrautheit, das direkt mit der Zeit und der Arbeit korreliert, die der Nutzer in das Erlernen und die Nutzung der Technologien investiert. Dieses Spektrum reicht von unerfahrenen bis hin zu erfahrenen Nutzern. Die Vorteile beider Technologien können am besten von erfahrenen Nutzern genutzt werden. Menschen, die in der Lage sind, die Erkenntnisse aus ihren Erfahrungen zu nutzen und sie erfolgreich auf ihr Leben anzuwenden, profitieren am meisten.
Diese Fähigkeit, Erkenntnisse zu erkennen, zu nutzen und in die Tat umzusetzen, würde ich als fortgeschrittene Nutzung von Psychedelika bezeichnen. Viele Menschen, die Psychedelika einnehmen, gelangen zu tiefgreifenden Einsichten, die eine große persönliche Bedeutung haben. Wenn die Wirkung nachlässt, setzen unerfahrene Nutzer diese Erkenntnisse jedoch nicht in die Tat um.
Vorteile, Entdeckungen und Erfindungen können sich in einem Funken der Inspiration manifestieren, nur um wenige Augenblicke später wieder vergessen und für immer verloren zu sein. Manche Nutzer erleben nach einer psychedelischen Erfahrung Veränderungen, aber die sind nur von kurzer Dauer. Sie gewinnen Einsichten und nehmen Veränderungen vor, aber wie viele Neujahrsvorsätze verschwinden diese schnell in der Entropie. Die Veränderungen halten ein paar Wochen, vielleicht einen Monat an, aber schon bald fallen die Nutzer wieder in die Routine des Alltags zurück und schlechte Gewohnheiten, die erkannt und angegangen wurden, kehren zurück.
Die Rückkehr des Alltäglichen und das Aufzwingen der Welt auf unsere Gewohnheiten kann eine mächtige Kraft sein. Psychedelische Drogen und die Erkenntnisse aus den ersten Prinzipien des Bitcoin-Denkens können mächtig sein, müssen aber verstärkt werden. Diese Verstärkung kann in Form von direktem Handeln, tiefem Studium oder Willenskraft erfolgen, aber ich glaube, dass es auch wichtig ist, zur Quelle der Erfahrung zurückzukehren.
Für Bitcoin bedeutet das, Podcasts zu hören, zu lernen, zu programmieren, zu bauen und zu teilen. Bei psychedelischen Drogen bedeutet das, dass du die psychedelische Erfahrung in regelmäßigen Abständen wiederholen musst. Es gibt kein Patentrezept. Du würdest nicht erwarten, dass eine einzige Dosis Aspirin ein Leben lang Schmerzen lindert, und mit Psychedelika ist es genauso. Sie wirken eine Zeit lang, sollten aber nur bei Bedarf verabreicht werden.
Es ist von größter Bedeutung, die während einer psychedelischen Erfahrung gelernten Lektionen oder gewonnenen Erkenntnisse richtig zu verarbeiten. Wenn du während der Erfahrung etwas Wertvolles bekommst, behandle es wie jeden anderen Gegenstand von großem Wert. Du wirst nicht bei jedem Erlebnis Einsichten oder Lebenslektionen erhalten, und das ist in Ordnung. Aber es ist gut, darauf vorbereitet zu sein, wenn sie auftauchen, damit du ihren Wert für dein Leben maximieren kannst.
Selbstvertrauen aufbauen
\ Sowohl Bitcoin als auch Psychedelika können ein tiefes inneres Vertrauen aufbauen. Psychedelische Drogen können sehr herausfordernd sein. Die psychedelische Erfahrung kann in gewisser Weise mit einer Initiation verglichen werden. Manche Menschen erleben auf Psychedelika eine Tod-Wiedergeburt-Erfahrung, und es gibt keine lebensbejahendere Erfahrung als die eines Nahtods.
Psychedelika können auch sehr beängstigend sein, wenn sie ohne die nötige Vorsicht und den nötigen Respekt eingesetzt werden. Aber selbst die furchterregendsten Erfahrungen bringen uns nicht um, und das gibt uns ein Gefühl der Ermächtigung. Auch ohne das Drama des Egotods oder eine beängstigende psychedelische Erfahrung würden viele Menschen einen Teil ihrer psychedelischen Erfahrung als „herausfordernd" bezeichnen. Diese tiefgreifenden inneren Herausforderungen zu durchlaufen, kann das Selbstvertrauen enorm stärken.
Die psychedelische Erfahrung ist auch eine moderne Analogie zu einer inneren „Heldensuche". Sie wird nicht auf die leichte Schulter genommen und ist ein Weg mit großen persönlichen Herausforderungen und Dramen. Die Suche kann zu einer direkten göttlichen, mystischen Erfahrung führen, zu einem Schatz, bevor der Held nach Hause zurückkehrt.
Bitcoin schafft auch ein Vertrauen, das man nur durch Erfahrung gewinnen kann. Diejenigen, die sich seit mehr als einem Jahr mit Bitcoin beschäftigen, sind auf zahlreiche Medienartikel gestoßen, die laut und stolz verkündeten: „Bitcoin ist tot!" Mehr als 450 dieser Artikel wurden in den letzten zehn Jahren veröffentlicht, doch Bitcoin stirbt nie. Er ist einer nicht enden wollenden Flut von technologischen, politischen und ideologischen Angriffen ausgesetzt, aber im Durchschnitt wird alle 10 Minuten ein neuer Bitcoin-Block im Netzwerk erzeugt. Die Uhr tickt weiter. Diese Widerstandsfähigkeit schafft Vertrauen bei den Bitcoinern, und dieses Vertrauen wächst und vertieft sich mit der Zeit.
Auswirkungen auf langfristiges Denken und Planen
\ Das Konzept der „Zeitpräferenz", das von Saifedean Ammous populär gemacht wurde, basiert auf den Entscheidungen, die wir alle treffen, und ihrem Verhältnis zur Zeit. Willst du einen Bitcoin heute oder zehn im nächsten Jahr?
Es gibt zwei Arten von Zeitpräferenzen: hohe und niedrige. Das Denken mit hoher Zeitpräferenz optimiert für die unmittelbare Zukunft (heute, morgen), während das Denken mit niedriger Zeitpräferenz für die lange Zukunft (Jahre, Jahrzehnte, Generationen) optimiert. Das Denken in niedrigen Zeitpräferenzen ist ein Luxus, den sich diejenigen leisten, die ihre unmittelbare Zukunft gesichert haben. Man kann nicht für die Zukunft planen, wenn man nicht weiß, woher die nächste Mahlzeit kommt oder wo man die Nacht verbringen wird.
Zum Denken mit geringen Zeitpräferenzen gehört das Sparen für die Zukunft und die Sicherung des persönlichen Wohlstands durch große persönliche Verantwortung und Bildung. Diejenigen, die in Bitcoin sparen und sie langfristig halten, stellen fest, dass ihr Vermögen um Größenordnungen zunimmt. Niemand hat jemals Bitcoin gekauft, sie vier Jahre lang gehalten und dann Geld verloren. Niemals. Das passiert einfach nicht. Wenn du sie kurzfristig kaufst, kann alles Mögliche passieren, und höchstwahrscheinlich wirst du dein Geld verlieren. Kaufe, halte, sammle und gib sparsam aus.
Diese Lehren aus dem Bitcoin beginnen das Leben der Nutzer zu durchdringen, und schon bald wird diese Art des Denkens auf alle Aspekte des Lebens angewendet. Die Nutzer bilden sich in verwandten Disziplinen weiter, treiben Sport und ernähren sich gesünder, weil sie nun optimistischer in die Zukunft blicken.
Eine düstere Zukunft, die einst voller Ungewissheit war, wird durch persönliches Handeln in eine Vision der Hoffnung verwandelt, und das ist unbeschreiblich ermutigend.
Es kommt niemand, um dich zu retten. Du musst der Held auf dieser Reise sein.
Psychedelika wirken sich sowohl auf das Denken in niedrigen als auch in hohen Phasen aus und sind für jeden Menschen zutiefst individuell. Ich finde, dass Psychedelika als persönliches Barometer genutzt werden können - ein Werkzeug, um den Verlauf meiner Zukunft vorherzusagen. Indem wir die Vergangenheit nutzen, um aus einzigartigen und unverwirklichten Perspektiven in die Zukunft zu blicken, können wir dieses Werkzeug nutzen, um Pläne für persönliches Wachstum zu entwerfen. Indem ich mich außerhalb meiner alltäglichen Erfahrungen bewege, kann ich mich aus einem ganz neuen Blickwinkel betrachten.
Viele von uns können schnell die Fehler anderer sehen, aber nicht die eigenen? Psychedelika ermöglichen uns einen Perspektivwechsel, der es uns erlaubt, uns selbst und unser Leben aus einem neuen Blickwinkel zu betrachten, in dem wir Fehler, die wir ignoriert, übersehen oder unterdrückt haben, leicht und klar erkennen können.
Ich kann das Ziel und den Weg dorthin sehen. Ich kann sehen, was für mich richtig ist, und ich kann auch andere Wege sehen, die ich einschlagen könnte und wo sie mich in die Irre führen könnten. Die wahre Kraft der Psychedelika besteht darin, diese Einsichten zu erkennen und konsequent danach zu handeln. Viele Menschen nehmen Psychedelika und haben eine großartige Vision, stecken dann aber zwei Wochen später in denselben persönlichen und emotionalen Furchen fest, in denen sie vor der Erfahrung steckten. Das liegt daran, dass es fast keine guten Informationen über die richtige Integration psychedelischer Erfahrungen gibt. Deine beste Lehrerin oder dein bester Lehrer ist es, die Arbeit zu machen, aufmerksam zu sein, sich entsprechend anzupassen und die Ergebnisse zu beobachten. Tatsache ist, dass viele Menschen durch den Konsum von Bitcoin und/oder Psychedelika langfristige positive Veränderungen in ihrem Leben bewirken.
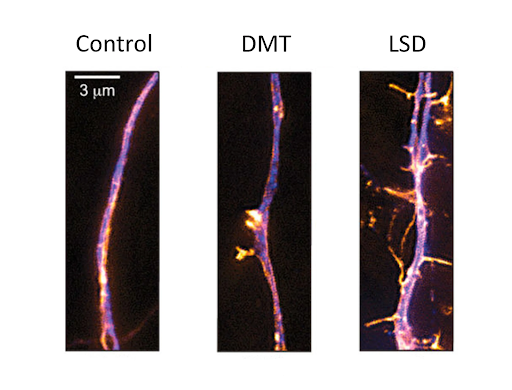
Die Wirkung von Psychedelika findet nicht nur im Kopf statt. Die Wissenschaft hat gezeigt, dass diese Moleküle die Struktur unseres Gehirns physisch verändern. Dieses Bild zeigt, wie Psychedelika das Wachstum von Gehirnzellen fördern und neue Nervenbahnen im Gehirn bilden können. Du denkst anders, weil du anders bist.
Altcoins, Forschungschemikalien und Schadensminimierung
\ Sowohl bei Bitcoin als auch bei Psychedelika gibt es räuberische „Hochstapler" und Affinitätsbetrüger, die auftauchen, um die Gemeinschaft auszunutzen. In beiden Kulturen gibt es eine unehrliche Bevölkerung, die von der Förderung dieser Betrügereien profitiert, und eine ehrliche Bevölkerung, die als Immunsystem fungiert, um diese Gifte zu identifizieren, zu entlarven und zu vertreiben. Bei Bitcoin gibt es eine aktive Kultur, die den Affinitätsbetrug schnell, laut und nachdrücklich aufdeckt. In der Psychedelik gibt es eine ähnliche Kultur, die „Schadensminimierung" genannt wird und in der lautstarke Mitglieder die größere Gemeinschaft vor den Angriffen der schlechten Akteure schützen.
Es gibt eine ganze Galaxie von „Altcoins", die behaupten, dass sie aus dem einen oder anderen Grund besser sind als Bitcoin. Einige der Altcoin-Projekte mögen legitime Experimente mit digitalen Vermögenswerten sein, aber die große Mehrheit sind gefährliche Betrüger, die versuchen, dein Geld durch falsche Versprechungen und technisches Geschwätz zu stehlen.
Diese Altcoins nehmen viele Formen an: Defi, Proof-of-Stake, algorithmische Stablecoins, NFTs und viele andere Worthülsen, die bei näherer Betrachtung nicht das sind, wofür sie werben. Viele dieser Projekte und Altcoins behaupten, sie seien „dezentralisiert", während sie in Wirklichkeit direkte zentralisierende Faktoren verbergen, die den gesamten Sinn des Projekts zunichte machen. In Bitcoin haben wir einen umgangssprachlichen Ausdruck für diese Nicht-Bitcoin-Krypto-Vermögenswerte: Shitcoins.
"Es gibt Bitcoin und es gibt Shitcoin."- Kongressabgeordneter Warren Davidson

\ Eine ganze Galaxie von psychedelischen Molekülen aus dem Frankenstein'schen Zeitalter findet ihren Weg aus skizzenhaften Laboren in Übersee auf die globalen psychedelischen Märkte. Dinge wie 2C-I, DOB, aMT, 25i-NBOMe, Bromo-Dragonfly und JWH-018 sind nur einige der chemischen Substanzen, die derzeit auf dem Weltmarkt erhältlich sind.
Weil diese Chemikalien so selten sind, gibt es nur sehr wenige Daten über ihr Sicherheitsprofil. Skrupellose Dealer kaufen diese billigen Imitate und verkaufen sie als LSD, MDMA oder Meskalin an ahnungslose Kunden. 25i-NBOME wird oft fälschlicherweise als LSD verkauft, aber diese Substanz ist hochgiftig und hat schon mehrere Konsumenten getötet, im Gegensatz zu LSD, das noch nie jemanden getötet hat.
Ich habe ein paar Blotter zur Schadensminimierung erstellt, um diese betrügerische Technik zu bekämpfen. Dies ist ein Beispiel dafür, dass der Aktivismus zur Schadensbegrenzung Parallelen zum „toxischen Bitcoin-Maximalismus" aufweist.
Obwohl es in beiden Gemeinschaften überall Betrüger gibt, ist nicht jeder, der sich mit Altcoins oder Forschungschemikalien beschäftigt, unehrlich oder darauf aus, dir zu schaden. Viele erforschen ernsthaft die Vorzüge und Fallstricke dieser unbekannten Wege, und ich habe nichts dagegen, dass sie das tun. Diese Menschen sind nicht gefährlich für die Gemeinschaft, sondern meist nur für sich selbst.
Auch wenn ich glaube, dass sie fehlgeleitet sind, schaden ihre ehrlichen Erkundungen niemandem. Manche Menschen investieren einen großen Teil ihres Lebens in die Erkundung dieser Pfade und finden vielleicht nie den Weg hinaus. Ich denke jedoch, dass dies für die meisten ein Übergangsstadium ist, in dem sie die Konsequenzen ihres falschen Denkens erfahren und sich selbst korrigieren.
Wenn die Selbsterkundung zur Anpreisung wird, haben wir eine Grenze überschritten. Ich habe etwas dagegen, wenn Menschen falsche Behauptungen aufstellen, die für jeden, der ihnen zuhört, gefährliche Folgen haben, vor allem, wenn sie das nur tun, weil sie davon profitieren.
Sowohl bei Bitcoin als auch bei Psychedelika gibt es ausgetretene Pfade, die zuverlässig und vorhersehbar sind. Andere Wege sind weniger ausgetreten oder sogar unbekannt und bergen neue und einzigartige Gefahren. Die klassischen Psychedelika wie LSD, Pilze, DMT, Meskalin und Cannabis sind gut befahrene, gut dokumentierte und entsprechend gekennzeichnete Wege. Das bedeutet, dass Millionen von Menschen diese Substanzen über Jahrzehnte oder sogar Jahrhunderte hinweg konsumiert haben. Aufgrund ihrer weit verbreiteten, langfristigen Verwendung wissen wir viel über ihre Sicherheit, Wirksamkeit und Dosierung. Diese Psychedelika sind in einer Vielzahl von Umgebungen unglaublich sicher.
Bitcoin ist auch ein weit verbreiteter Weg. Er hat Millionen von Nutzern und ist seit über einem Jahrzehnt in der Praxis erprobt. Bitcoin winkt jeden Tag mit einem Billionen-Dollar-Preis für jeden, der ihn knacken kann, doch niemand hat es je geschafft. Das Gegenteil ist in der Welt der Nicht-Bitcoin-Kryptowährungen der Fall. Fast wöchentlich gibt es einen neuen Defi- oder Smart-Contract-Exploit oder Hack. Der Sommer 2022 hat uns auch gezeigt, wie gefährlich es ist, Dritten zu vertrauen und ein Gegenparteirisiko einzugehen.
Die wichtigste Erkenntnis aus diesem Abschnitt, wenn nicht sogar aus dem ganzen Artikel, ist, dass man sich in der Welt der "Kryptowährungen" auf Bitcoin konzentrieren sollte, wie auf LSD und Psilocybin in der Welt der Psychedelika.\ \ Es gibt viele Ablenkungen und falsche Wege, die dich in die Irre führen. Fallen Sie nicht darauf herein. Sowohl Psychedelika als auch Bitcoin zeigen uns, dass Zeit unser wertvollstes Gut ist. Wenn du den Fokus verlierst, ist es leicht, von der Mission abzuweichen und dich ablenken zu lassen. Wenn du deine Aufmerksamkeit und Energie fokussierst, verbringst du mehr Zeit auf Wegen, die tiefgreifende und messbare Vorteile für dein Leben haben können. Du kannst nicht gewinnen, wenn du nicht spielst. Ablenkungen halten dich komplett vom Spielfeld fern.
Es gibt kein "Wundermittel" gegen falsches Denken
\ Viele Nutzer von Psychedelika glauben, dass sich alles innerhalb eines Nachmittags ändern würde, wenn alle Menschen auf der Welt LSD nehmen würden. Bei Bitcoin gibt es den Spruch „Bitcoin repariert dies", der besagt, dass Bitcoin auf magische Weise fast jedes Problem auf der Welt lösen kann. Meiner Erfahrung nach gibt es leider kein Patentrezept für falsches Denken.
Bitcoin hält die Shitcoinerei nicht auf. Psychedelische Drogen machen dich nicht automatisch zu einem guten Menschen.
Nur weil du dich für Bitcoin interessierst, heißt das nicht, dass du gegen Fiat-Denken oder Shitcoinerei immun bist. Und nur weil du Psychedelika nimmst, heißt das nicht, dass du nicht in einem Labyrinth aus fantastischem Denken landest. Es bedeutet auch nicht, dass du deine psychedelischen Erkenntnisse erfolgreich in dein Leben integrieren wirst.
Als ich mit Bitcoin anfing, hatte ich keine Ahnung von der riesigen Welt der Kryptowährungen. Ich dachte, Bitcoin sei die einzige digitale Währung. Ich fand schnell heraus, dass es über tausend verschiedene „Altcoins" gibt. Ich begann zu recherchieren, aber die verfügbaren Quellen waren nicht zuverlässig. Ich sah immer wieder Altcoin-Promoter, die sagten: „Bitcoin ist eine alte, veraltete Technologie", „Bitcoin ist langsam und teuer" und „dieser neue Coin behebt all das".
Noch wichtiger ist, dass diese Betrüger von dem Wunschtraum leben, dass diese neue Münze das gleiche Wachstum wie Bitcoin erfährt und möglicherweise den Nutzen und den Preis von Bitcoin übertrifft. Oft kosten diese Münzen nur ein paar Cent pro Stück, so dass die Verlockung, ein paar Cent in Zehntausende zu verwandeln, wie ein Sirenengesang auf unsere Gier wirkt.
Ich bin darauf hereingefallen und habe über ein Jahr lang auf die harte (und teure) Tour gelernt, dass ich meine Zeit und mein Geld mit einem Haufen Shitcoins verschwendet habe. Das war eine wertvolle, aber teure Lektion. Ich habe sie mir zu Herzen genommen und konzentriere mich jetzt ausschließlich auf Bitcoin. Das hat mein Leben in vielerlei Hinsicht verändert und dafür bin ich für immer dankbar.
Das spricht dafür, dass einige von uns die Dinge auf die harte Tour lernen müssen. Man kann keine Einsicht gewinnen, ohne die Erfahrung gemacht zu haben, Zeit, Energie und Geld zu verlieren. Für manche sind das die Kosten für das Schulgeld. Ich hoffe, dass du aus meinen Fehlern lernen kannst. Ich kann dir empfehlen, die Twitter-Seite von @CoinFessions zu besuchen, wenn du aus den Fehlern anderer lernen willst. Heute bin ich sehr schnell dabei, meine Zeit und Aufmerksamkeit auf meine spezielle Mission zu konzentrieren und so viele Ablenkungen auszuschließen, wie ich abwehren kann.
Hüte dich vor der „Touristen"-Kultur
\ Bezahlte Krypto-Tradinganalyse-Gruppenleitern und Ayahuasca-Schamanen sollten mit größter Skepsis betrachtet werden. In fast allen Fällen sollte man diese Leute meiden. Das gilt auch für Ayahuasca-Tourismus, psychedelische Exerzitien, medizinisch unterstützte psychedelische Behandlungen und jede Situation, in der du deine Souveränität, deinen Platz und dein Umfeld an andere abgibst.
Ich möchte nicht beobachtet, angeleitet oder angesungen werden oder die Protokolle, Glaubenssätze oder Rituale anderer auf mich projiziert bekommen, während ich mich in einem psychedelischen Zustand befinde. Ich möchte die Kontrolle über meine eigene Erfahrung haben und diese Verantwortung nicht an eine vertrauenswürdige dritte Person abgeben. Das Gleiche gilt für das Vertrauen in einen YouTube-Krypto-Trader, der finanzielle Entscheidungen trifft, die mich und meine Familie betreffen. Das wird nicht passieren.
Wenn du irgendwo im Urlaub bist, wissen wir alle, dass es eine „Touristenversion" und eine „echte Version" der Orte gibt, die wir besuchen. Es gibt den Strand, an den du gereist bist, mit dem herrlichen Sand, der Sonne und dem Himmel, und dann gibt es den Laden, der versucht, dir T-Shirts, Muscheln, Schlüsselanhänger und eine Fahrt im Kleinbus zu verkaufen, um die örtlichen Sehenswürdigkeiten zu sehen.
Geh an den Strand und halte dich von den Touristenläden fern. In jeder Kultur gibt es Elemente, die "wahr und rein" für die Ideologien der Bewegung sind. Es gibt aber auch räuberische Mitläufer, die nach Gelegenheiten suchen, die Unwissenheit der Neuankömmlinge über die Feinheiten auszunutzen.
In der Bitcoin-Kultur gibt es das Konzept des „Orangewashings", mit dem man sich als Bitcoiner ausgibt, aber in Wirklichkeit ist man ein Shitcoiner oder Betrüger, der nur so tut, als ob er so tut, als ob er so tut und so redet. Andere machen sich gar nicht erst die Mühe des Orangenwaschens und verkünden stolz, dass Bitcoin alt, langsam, Boomer-Tech und eindeutig minderwertiger als ihre neueste Version ihres Schlangenöls ist.
In der psychedelischen Kultur gibt es immer mehr Menschen, die dein Geld gerne annehmen, um dir im Gegenzug psychedelische Dienstleistungen, Moleküle und sogar Investmentaktien anzubieten. Manche haben tiefere und dunklere Beweggründe für deinen Geist und Körper. Ich würde dir raten, dich von all diesen Angeboten fernzuhalten oder sie zumindest mit großer Skepsis zu betrachten. Ich sage nicht, dass alle Erscheinungsformen dieser Aspekte der Kulturen von Natur aus schädlich sind, sondern dass man immer die Anreize im Auge behalten muss. Wenn du dich auf einen Rückzugsort, einen „Schamanen", einen psychedelischen Arzt oder eine Fachkraft einlässt, dann recherchiere ausgiebig über die Person/das Unternehmen.
Nimm dir die Zeit, eine authentische Kultur zu suchen. Pflege das Echte und lehne das Gefälschte ab.\ \ Du wirst um ein Vielfaches belohnt werden, und zwar auf unvorhersehbare Weise.
Alchemie
\ Ich möchte auf die Verbindung zum alten alchemistischen Wunsch eingehen, Blei in Gold zu verwandeln. Mit Bitcoin verwandeln wir die Fiat-Strukturen der Welt in einen digitalen, kryptografischen Schatz, der sich überall auf der Welt hin teleportieren kann. Dies geschieht wie ein Zauberspruch, indem man bestimmte Wörter in der richtigen Reihenfolge verwendet. Wenn du den Code ausführst, funktioniert er. Indem wir die richtigen Wörter in der richtigen Reihenfolge verwenden, können wir die Welt wesentlich verändern.
Das sind nicht nur Veränderungen in unseren Köpfen. Es sind Veränderungen, die andere sehen, fühlen und unabhängig überprüfen können. Der richtige Computercode kann eine Zugbrücke anheben oder alle Ampeln in der Stadt in perfektem Timing ändern, damit die Autofahrer sicher über die Straßen kommen. Bitcoiner sind Magier und Zauberer, die Computercode statt Zauberbücher benutzen. Psychedelische Chemiker sind Zauberer, die ihre Zaubersprüche in der Sprache der Atome sprechen. Wie Buchstaben, die Wörter in einem Code oder einem Zauberspruch bilden, werden Atome zu Molekülen angeordnet.
Psychedelika verwandeln das fiktive Denken und Leben in neue Perspektiven und mystische Erfahrungen. Pilze sind wie die Alchemisten der Natur - sie verwandeln tote und verfallende Materie, also buchstäblichen Müll, in psychedelische Pilze, eine der elegantesten Erscheinungsformen der Natur.
Bitcoin kann auch Abfall in Schätze umwandeln. Gestrandete Energie, einst eine Last, wird durch Bitcoin in eine digitale Goldmine verwandelt. Bitcoin kann sogar unsere Mülldeponien in wertvolle Bitcoin-Minen verwandeln und so Müll in Schätze verwandeln. Der alchemistische Traum wird wahr, und zwar auf eine Weise, die sich unsere Vorfahren nie hätten vorstellen können.
Die alte Wissenschaft und Chemie der Alchemie findet im digitalen Zeitalter eine neue Form. Wenn du diese Werkzeuge studierst und anwendest, kannst du dein Leben und die Welt um dich herum wirklich und dauerhaft verändern.
"Es handelt sich eindeutig um eine Krise von zwei Dingen: des Bewusstseins und der Konditionierung. Wir haben die technologische Macht, die technischen Fähigkeiten, um unseren Planeten zu retten, Krankheiten zu heilen, die Hungernden zu ernähren und Kriege zu beenden. Aber es fehlt uns an der intellektuellen Vision, an der Fähigkeit, unsere Meinung zu ändern. Wir müssen uns von 10.000 Jahren schlechten Verhaltens befreien. Und das ist nicht einfach." - Terence McKenna
\ ⚡ Unglaublich, du hast den Artikel bis zum Ende gelesen und ich hoffe du konntest etwas Mitnehmen für deine persönliche Reise aus diesem Text.\ \ ⚡ Vielen Dank für deine Aufmerksamkeit. Wenn dir die kostenfreie Übersetzung dieses Artikels gefallen hat, würde ich mich über ein paar Satoshi auf Value for Value Basis freuen.
-
 @ 04ea4f83:210e1713
2025-05-01 18:18:36
@ 04ea4f83:210e1713
2025-05-01 18:18:36Digitales Geld ist nur Text, die ganze Zeit
Bei digitalem Geld geht es im Grunde nur um Zahlen in einem Hauptbuch. Die ganze Zeit über sind es die Zahlen, auf die es ankommt. Lange Zahlen sind einfach nur Zeichenketten im PC und diese werden als Nachrichten in einem Netzwerk, das durch Regeln gebildet wird, an gleichwertige Peers gesendet - das ist Bitcoin, das mit einem einzigartigen dezentralen Zeitstempel-Algorithmus kombiniert wird, der durch die Unfälschbarkeit von Energie gesichert ist. Das Ergebnis ist ein Bargeldnetzwerk mit einem festen, vorprogrammierten Zeitplan für die Geldschöpfung, das den ersten absolut knappen digitalen Inhabervermögenswert schafft.\ \ Diese revolutionären Ideen werden bleiben, genauso wie das Feuer, das Rad, die Elektrizität, das Smartphone, das Internet oder die Zahl Null. Technologie entwickelt sich weiter und was machen lebende Organismen? Sie können mutieren, genau wie Viren, und das hat mich zu dem Schluss gebracht, dass es auch in dieser Hinsicht eine Verbindung gibt und das obwohl Gigi bereits einige der vielen Facetten von Bitcoin beschrieben hat. Für mich ist die Grundlage die Abstraktion, dass Bitcoin nur die Summe aller Menschen ist, die Satoshis besitzen oder anderweitig mit dem Bitcoin-Netzwerk interagieren.\ \ Die Technologien werden in einem bestimmten Tempo angenommen. Allerdings gibt es immer frühe oder späte Entdecker von neuer Technologie. Aber was passiert, wenn es zu einer ernsthaften Bedrohung wird, wenn hartes Geld nicht adoptiert wird? Was passiert, wenn die Geschwindigkeit der Preiszunahme so hoch wird, dass es unmöglich ist, jemanden zu finden, der Satoshi in Fiat tauschen möchte? Was passiert, wenn die Hyperbitcoinisierung morgen beginnt? Was wäre, wenn es eine UpSideProtection™️ gäbe, die diesen Prozess noch mehr beschleunigt und dir Bitcoin zu einem Bruchteil seines wahren Wertes sichert?\ \ Wir alle wünschen uns einen sicheren Übergang, um den Krieg aufgrund einer scheiternden Dollar-Hegemonie zu vermeiden, und tatsächlich gibt es ein Rennen, um den Krieg zu vermeiden. Mein größtes Geschenk ist die Zeit, die ich ich investiere, und die monetäre Energie, die ich in Bitcoin spare, und da ich schon eine Weile dabei bin, sehe ich, dass meine Mitstreiter die gleiche Mission verfolgen. Aber das ist NICHT genug. Wir müssen skalieren. Schneller.\ \ Das Erstaunen über den Kurzfilm der große Widerstand hat mich zu dem Schluss gebracht, dass wir alle Werkzeuge und Informationen in Form von Lehrern, Podcasts, Büchern und aufklärenden Videos bereits haben. Der Vorteil einer festen Geldmenge wird aber noch nicht von einer kritischen Masse verstanden, sondern nur von einer intoleranten Minderheit. Diese Minderheit wächst von Tag zu Tag. Ihre Inkarnationen sind die DCA-Armee, die Hodler der letzten Instanz, die unbeirrten Stacker, die Cyberhornets, die Memefactory™️ und Mitglieder der 21 Gruppe auf der ganzen Welt.\ \ Wir Bitcoiner sind räumlich getrennt, aber nicht in der Zeit. Getrennt in der Sprache, aber nicht in der Mission. Vereint müssen wir uns zu Wort melden, aufklären und Bitcoin wie einen Virus verbreiten.\ \ Niemand entscheidet, was Bitcoin für dich ist - dieser Virus des Geistes verfestigt sich in unbestechlichen Zahlen, die zu einer wachsenden Zahl an UTXOs in den Geldbörsen führen, nicht in negativen gesundheitlichen Auswirkungen. Bitcoin ist der Virus der Schuldenindustrie, der Virus, der im 21. Jahrhundert zur größten Definanzialisierung und Auflösung des Kredits führen wird. Da wir noch nicht in einer hyperbitcoinisierten Welt leben, müssen wir den Virus effektiver machen. Bitcoin muss mutieren, aber es ist nicht Bitcoin, der tatsächlich mutiert, sondern die Menschen, die ihn benutzen. Sie werden zu toxischen Maximalisten, die den Virus noch stärker verbreiten und alle Shitcoiner während ihrer Anwesenheit geistig infizieren oder argumentativ töten.\ \ Ich habe mich gefragt, wie wir eine Milliarde Menschen dazu ausbilden und überzeugen können, Bitcoin freiwillig zu nutzen und darin zu sparen, so dass sie Bitcoin als primäres Mittel zur Speicherung und Übermittlung von Werten in Raum und Zeit nutzen? Die Hyperbitcoinisierung braucht nur eine einzige, starke positive Rückkopplungsschleife um wirklich in Gang zu kommen, und diese Rückkopplung gibt es bereits, aber nicht in den Köpfen aller. Ab einer bestimmten Schwelle wird die Schwerkraft von Bitcoins gehärteten monetären Eigenschaften einfach zu hoch sein, als dass die Spieltheorie nicht zu dieser Rückkopplung führen würde, vor allem da Bitcoin im Jahr 2024 Gold in Punkto Knappheit übertrifft.\ \ Die Verbreitung der Idee einer festen dezentralen Geldmenge, die der Macht zentraler Kräfte entzogen ist, ist der Virus. Der Weg, das Spiel zu spielen, ist, Stacker zu stapeln, und Stacker stapeln Sats, wodurch die Geldmenge noch dezentralisierter wird und ein Verbot noch absurder wird. Sats sind endlich und unser Spiel ist es auch. Allein eine bestimmte Anzahl von einfachen Leuten, den Plebs, kann den Preis auf 1.000.000 EURO treiben.\ \ Letztendlich wird sich die Welt an das neue Gleichgewicht der Macht zugunsten des Individuums anpassen. Diese Idee in die Köpfe der Massen zu bringen, ist die wichtigste Aufgabe für 2023, die in das nächste Halving Mitte 2024 führt.\ \ Wir müssen unseren Reproduktionswert erhöhen, um die Akzeptanz zu steigern. Die Verwendung von Bitcoin als Zahlungsmittel und eine Kreislaufwirtschaft ist wichtig. Bildung ist wichtig. Apps und Anwendungsfälle sind wichtig. Die Kaufkraft, d.h. die Moskau Zeit, die sich in Richtung Mitternacht (00:00) bewegt, spielt eine Rolle, und all dies hängt zusammen.\ \ Aber wie genau können Plebs eine Milliarde Menschen überzeugen?\ \ Wie genau hat das Corona-Virus eine Milliarde Menschen infiziert?\ \ Peer-to-Peer.\ \ Erhebe deine Stimme, wer auch immer du bist, sprich über Bitcoin, werde aktiv und BUIDL oder lass uns einfach Spaß daran haben, arm zu bleiben und es genießen, jeden Tag bestohlen zu werden.\ \ Lass uns Yellow mehr Freizeit schenken und Bitcoin bis 100k+ aufkaufen und uns damit ins Stackheaven befördern.
"Don't stop believin' HODL on to that feelin' "
Der Rest wird in die unumstößliche Geschichte der Timechain eingraviert.
„Unter dieser Maske gibt es mehr als nur Fleisch. Unter dieser Maske ist eine Idee. Und Ideen sind kugelsicher." Alan Moore, V wie Vendetta

⚡
Danke für deine Aufmerksamkeit .\ \ #GetShortFiat und #GetOnZero\ \ Es ist immer noch 60 Uhr. Sei weise und stapele unbeirrt. Man kann die Mathematik und Physik nicht austricksen.\ \ Wenn der Post dir Motivation zum Stapeln von Sats oder dem Stapeln von Stackern gemacht hat, freue ich mich, wenn du mir auch etwas beim Stapeln hilfst!
-
 @ d34e832d:383f78d0
2025-04-26 04:24:13
@ d34e832d:383f78d0
2025-04-26 04:24:13A Secure, Compact, and Cost-Effective Offline Key Management System
1. Idea
This idea presents a cryptographic key generation appliance built on the Nookbox G9, a compact 1U mini NAS solution. Designed to be a dedicated air-gapped or offline-first device, this system enables the secure generation and handling of RSA, ECDSA, and Ed25519 key pairs. By leveraging the Nookbox G9's small form factor, NVMe storage, and Linux compatibility, we outline a practical method for individuals and organizations to deploy secure, reproducible, and auditable cryptographic processes without relying on cloud or always-connected environments.
2. Minimization Of Trust
In an era where cryptographic operations underpin everything from Bitcoin transactions to secure messaging, generating keys in a trust-minimized environment is critical. Cloud-based solutions or general-purpose desktops expose key material to increased risk. This project defines a dedicated hardware appliance for cryptographic key generation using Free and Open Source Software (FOSS) and a tightly scoped threat model.
3. Hardware Overview: Nookbox G9
| Feature | Specification | |-----------------------|----------------------------------------------------| | Form Factor | 1U Mini NAS | | Storage Capacity | Up to 8TB via 4 × 2TB M.2 NVMe SSDs | | PCIe Interface | Each M.2 slot uses PCIe Gen 3x2 | | Networking | Dual 2.5 Gigabit Ethernet | | Cooling | Passive cooling (requires modification for load) | | Operating System | Windows 11 pre-installed; compatible with Linux |
This hardware is chosen for its compact size, multiple SSD support, and efficient power consumption (~11W idle on Linux). It fits easily into a secure rack cabinet and can run entirely offline.
4. System Configuration
4.1 OS & Software Stack
We recommend wiping Windows and installing:
- OS: Ubuntu 24.10 LTS or Debian 12
- Key Tools:
gnupg(for GPG, RSA, and ECC)ageorrage(for modern encryption)openssl(general-purpose cryptographic tool)ssh-keygen(for Ed25519 or RSA SSH keys)vault(optional: HashiCorp Vault for managing key secrets)pwgen/diceware(for secure passphrase generation)
4.2 Storage Layout
- Drive 1 (System): Ubuntu 24.10 with encrypted LUKS partition
- Drive 2 (Key Store): Encrypted Veracrypt volume for keys and secrets
- Drive 3 (Backup): Offline encrypted backup (mirrored or rotated)
- Drive 4 (Logs & Audit): System logs, GPG public keyring, transparency records
5. Security Principles
- Air-Gapping: Device operates disconnected from the internet during key generation.
- FOSS Only: All software used is open-source and auditable.
- No TPM/Closed Firmware Dependencies: BIOS settings disable Intel ME, TPM, and Secure Boot.
- Tamper Evidence: Physical access logs and optional USB kill switch setup.
- Transparency: Generation scripts stored on device, along with SHA256 of all outputs.
6. Workflow: Generating Keypairs
Example: Generating an Ed25519 GPG Key
```bash gpg --full-generate-key
Choose ECC > Curve: Ed25519
Set expiration, user ID, passphrase
```
Backup public and private keys:
bash gpg --armor --export-secret-keys [keyID] > private.asc gpg --armor --export [keyID] > public.asc sha256sum *.asc > hashes.txtStore on encrypted volume and create a printed copy (QR or hex dump) for physical backup.
7. Performance Notes
While limited to PCIe Gen 3x2 (approx. 1.6 GB/s per slot), the speed is more than sufficient for key generation workloads. The bottleneck is not IO-bound but entropy-limited and CPU-bound. In benchmarks:
- RSA 4096 generation: ~2–3 seconds
- Ed25519 generation: <1 second
- ZFS RAID-Z writes (if used): ~250MB/s due to 2.5Gbps NIC ceiling
Thermal throttling may occur under extended loads without cooling mods. A third-party aluminum heatsink resolves this.
8. Use Cases
- Bitcoin Cold Storage (xprv/xpub, seed phrases)
- SSH Key Infrastructure (Ed25519 key signing for orgs)
- PGP Trust Anchor (for a Web of Trust or private PKI)
- Certificate Authority (offline root key handling)
- Digital Notary Service (hash-based time-stamping)
9. Recommendations & Improvements
| Area | Improvement | |-------------|--------------------------------------| | Cooling | Add copper heatsinks + airflow mod | | Power | Use UPS + power filter for stability | | Boot | Use full-disk encryption with Yubikey unlock | | Expansion | Use one SSD for keybase-style append-only logs | | Chassis | Install into a tamper-evident case with RFID tracking |
10. Consider
The Nookbox G9 offers a compact, energy-efficient platform for creating a secure cryptographic key generation appliance. With minor thermal enhancements and a strict FOSS policy, it becomes a reliable workstation for cryptographers, developers, and Bitcoin self-custodians. Its support for multiple encrypted SSDs, air-gapped operation, and Linux flexibility make it a modern alternative to enterprise HSMs—without the cost or vendor lock-in.
A. Key Software Versions
GnuPG 2.4.xOpenSSL 3.xUbuntu 24.10Veracrypt 1.26+
B. System Commands (Setup)
bash sudo apt install gnupg2 openssl age veracrypt sudo cryptsetup luksFormat /dev/nvme1n1C. Resources
The Nookbox G9 epitomizes a compact yet sophisticated energy-efficient computational architecture, meticulously designed to serve as a secure cryptographic key generation appliance. By integrating minor yet impactful thermal enhancements, it ensures optimal performance stability while adhering to a stringent Free and Open Source Software (FOSS) policy, thereby positioning itself as a reliable workstation specifically tailored for cryptographers, software developers, and individuals engaged in Bitcoin self-custody. Its capability to support multiple encrypted Solid State Drives (SSDs) facilitates an augmented data security framework, while the air-gapped operational feature significantly enhances its resilience against potential cyber threats. Furthermore, the inherent flexibility of Linux operating systems not only furnishes an adaptable environment for various cryptographic applications but also serves as a compelling modern alternative to conventional enterprise Hardware Security Modules (HSMs), ultimately bypassing the prohibitive costs and vendor lock-in typically associated with such proprietary solutions.
Further Tools
🔧 Recommended SSDs and Tools (Amazon)
-
Kingston A400 240GB SSD – SATA 3 2.5"
https://a.co/d/41esjYL -
Samsung 970 EVO Plus 2TB NVMe M.2 SSD – Gen 3
https://a.co/d/6EMVAN1 -
Crucial P5 Plus 1TB PCIe Gen4 NVMe M.2 SSD
https://a.co/d/hQx50Cq -
WD Blue SN570 1TB NVMe SSD – PCIe Gen 3
https://a.co/d/j2zSDCJ -
Sabrent Rocket Q 2TB NVMe SSD – QLC NAND
https://a.co/d/325Og2K -
Thermalright M.2 SSD Heatsink Kit
https://a.co/d/0IYH3nK -
ORICO M.2 NVMe SSD Enclosure – USB 3.2 Gen2
https://a.co/d/aEwQmih
Product Links (Amazon)
-
Thermal Heatsink for M.2 SSDs (Must-have for stress and cooling)
https://a.co/d/43B1F3t -
Nookbox G9 – Mini NAS
https://a.co/d/3dswvGZ -
Alternative 1: Possibly related cooling or SSD gear
https://a.co/d/c0Eodm3 -
Alternative 2: Possibly related NAS accessories or SSDs
https://a.co/d/9gWeqDr
Benchmark Results (Geekbench)
-
GMKtec G9 Geekbench CPU Score #1
https://browser.geekbench.com/v6/cpu/11471182 -
GMKtec G9 Geekbench CPU Score #2
https://browser.geekbench.com/v6/cpu/11470130 -
GMKtec Geekbench User Profile
https://browser.geekbench.com/user/446940
🛠️ DIY & Fix Resource
- How-Fixit – PC Repair Guides and Tutorials
https://www.how-fixit.com/
-
 @ d34e832d:383f78d0
2025-04-25 23:39:07
@ d34e832d:383f78d0
2025-04-25 23:39:07First Contact – A Film History Breakdown
🎥 Movie: Contact
📅 Year Released: 1997
🎞️ Director: Robert Zemeckis
🕰️ Scene Timestamp: ~00:35:00
In this pivotal moment, Dr. Ellie Arroway (Jodie Foster), working at the VLA (Very Large Array) in New Mexico, detects a powerful and unusual signal emanating from the star system Vega, over 25 light-years away. It starts with rhythmic pulses—prime numbers—and escalates into layers of encoded information. The calm night shatters into focused chaos as the team realizes they might be witnessing the first confirmed evidence of extraterrestrial intelligence.
🎥 Camera Work:
Zemeckis uses slow zooms, wide shots of the VLA dishes moving in synchrony, and mid-shots on Ellie as she listens with growing awe and panic. The kinetic handheld camera inside the lab mirrors the rising tension.💡 Lighting:
Low-key, naturalistic nighttime lighting dominates the outdoor shots, enhancing the eerie isolation of the array. Indoors, practical lab lighting creates a realistic, clinical setting.✂️ Editing:
The pacing builds through quick intercuts between the signal readouts, Ellie’s expressions, and the reactions of her team. This accelerates tension while maintaining clarity.🔊 Sound:
The rhythmic signal becomes the scene’s pulse. We begin with ambient night silence, then transition to the raw audio of the alien transmission. It’s diegetic (heard by the characters), and as it builds, a subtle score underscores the awe and urgency. Every beep feels weighty.
Released in 1997, Contact emerged during a period of growing public interest in both SETI (Search for Extraterrestrial Intelligence) and skepticism about science in the post-Cold War world. It was also the era of X-Files and the Mars Pathfinder mission, where space and the unknown dominated media.
The scene reflects 1990s optimism about technology and the belief that answers to humanity’s biggest questions might lie beyond Earth—balanced against the bureaucratic red tape and political pressures that real scientists face.
- Classic procedural sci-fi like 2001: A Space Odyssey and Close Encounters of the Third Kind.
- Real-world SETI protocols and the actual scientists Carl Sagan consulted with.
- The radio broadcast scene reflects Sagan’s own passion for communication and cosmic connectedness.
This scene set a new benchmark for depicting science authentically in fiction. Many real-world SETI scientists cite Contact as an accurate portrayal of their field. It also influenced later films like Arrival and Interstellar, which similarly blend emotion with science.
The signal is more than data—it’s a modern miracle. It represents Ellie’s faith in science, the power of patience, and humanity's yearning to not be alone.
The use of prime numbers symbolizes universal language—mathematics as a bridge between species. The scene’s pacing reflects the clash between logic and emotion, science and wonder.
The signal itself acts as a metaphor for belief: you can't "see" the sender, but you believe they’re out there. It’s the crux of the entire movie’s science vs. faith dichotomy.
This scene hits hard because it captures pure awe—the mix of fear, wonder, and purpose when faced with the unknown. Watching Ellie realize she's not alone mirrors how we all feel when our faith (in science, in hope, in truth) is rewarded.
For filmmakers and students, this scene is a masterclass in procedural suspense, realistic portrayal of science, and using audiovisual cues to build tension without needing action or violence.
It reminds us that the greatest cinematic moments don’t always come from spectacle, but from stillness, sound, and a scientist whispering: “We got something.”
-
 @ 04ea4f83:210e1713
2025-05-01 18:12:30
@ 04ea4f83:210e1713
2025-05-01 18:12:30Was ist ein Meme?
Bevor wir uns in die Materie vertiefen, sollten wir einen genaueren Blick auf die Begriffe werfen, mit denen wir es zu tun haben. Laut dem American Heritage Dictionary of the English Language ist ein Meme „eine Einheit kultureller Informationen, wie z. B. eine kulturelle Praxis oder Idee, die verbal oder durch wiederholte Handlungen von einem Geist zum anderen übertragen wird".
Der Begriff wurde von Richard Dawkins in seinem 1976 erschienenen Buch geprägt und ist eine Anspielung auf das Wort "Gen", die Einheit der biologischen Information, die sexuell von einem Organismus auf einen anderen übertragen wird.
Dawkins erkannte, dass kulturelle Informationen ähnlich wie biologische Informationen sind und sich genauso verbreiten und mutieren, wenn auch auf einer höheren Abstraktionsebene. Genau wie bei biologischen Informationen ist der ultimative Test für kulturelle Informationen das Überleben, und genau wie biologische Informationen müssen sie für die Umwelt geeignet sein, um sich zu verbreiten und am Leben zu gehalten zu werden.
Manche Ideen funktionieren einfach nicht, wenn sie fehl am Platz sind oder die Zeit nicht reif für sie ist. Sie werden schnell sterben, genau wie der sprichwörtliche Fisch auf dem Trockenen. Andere Memes funktionieren vielleicht eine Zeit lang, verblassen aber langsam durch allmähliche Veränderungen in der Umwelt oder brechen plötzlich durch die von ihnen ausgelösten destruktiven Rückkopplungsschleifen zusammen. Wie Gene verbreiten sich Meme langfristig nur dann, wenn sie für den Organismus und seine Umwelt von Nutzen sind.
„In der Wissenschaft der Ökologie lernt man, dass der Mensch nicht ein Organismus in einer Umwelt ist, sondern eine Organismus-Umwelt-Beziehung. Das heißt, ein einheitlicher Bereich des Verhaltens. Wenn man das Verhalten eines Organismus sorgfältig beschreibt, kann man das nicht tun, ohne gleichzeitig das Verhalten der Umwelt zu beschreiben... [...] Der Organismus ist nicht die Marionette der Umwelt, die von ihr herumgeschubst wird. Umgekehrt ist auch die Umwelt nicht die Marionette des Organismus, die vom Organismus herumgeschubst wird. Die Beziehung zwischen ihnen ist, um es mit John Deweys Worten zu sagen, transaktional."\ \ Alan Watts
Was hat das mit Bitcoin zu tun? Nun, du musst dich fragen, wie das Bitcoin-Netzwerk zustande kommt, und wenn du das tust, wirst du feststellen, dass Bitcoin sich nicht allzu sehr von den oben erwähnten Memen und Genen unterscheidet. Bitcoin ist ein instanziierter Computercode, ein digitaler Organismus, der die Menschheit dafür bezahlt, ihn am Leben zu erhalten, wie Ralph Merkle es so treffend formulierte. Die kumulative Arbeit, die in Bitcoins Timechain eingebettet ist, ist das, was Bitcoin real macht und was ihn von gewöhnlicher Information unterscheidet. Und von gewöhnlichen Computerprogrammen, was das betrifft. Genauso wie es einen Unterschied zwischen dir selbst und einem Ausdruck deiner DNA gibt, gibt es einen Unterschied zwischen dem Bitcoin-Code - den Memes, die er sich zu Nutze macht - und der realen Instanziierung von Bitcoin.
Das Bitcoin-Netzwerk instanziiert und validiert sich selbst alle 10 Minuten, Block für Block, wie ein Uhrwerk. Diese Blöcke sind die Informationseinheit, die übertragen wird, und ja, genau wie bei den Memen ist diese Information eine kulturelle Information. Die Tatsache, dass diese Information elektronisch übertragen wird, spielt keine Rolle; sie verkörpert immer noch den Kern der Bitcoin-Kultur, die Seele des Netzwerks. Und genau wie Memes wird diese Information durch wiederholte Aktionen von einem Knotenpunkt zum anderen übertragen. Und davor, von einem Geist zum anderen.
Im ökologischen Sinne handeln wir alle mit Bitcoin, und Bitcoin handelt mit uns. Wenn du von Bitcoin gehört hast, wenn du das Meme „21 Millionen" kennst, dann hat Bitcoin mit dir Geschäfte gemacht. Lange bevor du deine erste Bitcoin-Transaktion gemacht haben.
Memes und ihre Umgebung
Bitcoin sind Menschen, wenn es darauf ankommt. Ja, es ist Software, aber die Menschen müssen die Software ausführen und, was noch wichtiger ist, selbst entscheiden, was Bitcoin ist. Es gibt keine Autorität, wenn es um Bitcoin geht. So muss jeder für sich selbst herausfinden, was Bitcoin ist, und aus der Überschneidung der verschiedenen Standpunkte ergibt sich ein Konsens. Dies ist ein ständiger Prozess, denn es geht nicht nur darum, was Bitcoin derzeit ist, sondern auch darum, was Bitcoin sein könnte. Was Bitcoin sein sollte. Genau darum ging es im Blocksize War. Ein Kampf um die Seele von Bitcoin. Eine Meinungsverschiedenheit über die Zukunft und den ultimativen Zweck von Bitcoin. Ein Unterschied im memetischen Material, der letztendlich zu einer Spaltung des Protokolls führte, was wiederum zu einer Spaltung des Netzwerks und einer Spaltung der Kultur führte.
Aber auch ohne eine Spaltung, selbst wenn ein Konsens besteht, ist die Frage „was Bitcoin ist" nicht eindeutig zu beantworten.
Für dich mag das Lightning Network nicht wichtig sein, und es steht dir frei, eine Vor-SegWit-Version von Bitcoin zu betreiben. Für jemand anderen sind Dickbutts und Fürze auf der Blockchain vielleicht nicht wichtig, und er könnte sich entscheiden, eine Vor-Taproot-Version von Bitcoin zu verwenden (oder eine Version zu verwenden, die Ordnungszahlen (Ordinals) nicht respektiert). Bitcoin ist abwärtskompatibel, und Upgrades sind optional, gerade weil es keine Autorität gibt, die etwas vorschreibt.
So funktioniert Bitcoin, und so wird es immer funktionieren, weshalb Memes wichtig sind und warum es eigentlich durchweg Memes sind.
Um Bitcoin zu nutzen, muss man sich freiwillig entscheiden. Man muss zuerst von der Idee überzeugt werden, von der Idee, Sats zu akzeptieren, damit Fiat fallen zu lassen und Bitcoin zu erwerben. Erst wenn man davon überzeugt ist, dass elektronisches Bargeld mit einer (absolut) festen Menge nützlich sein könnte, wird man es akzeptieren oder damit sparen.
Das Meme „21 Millionen" kommt zuerst, und nachdem unsere Gehirne ausreichend von der Idee infiziert wurden, werden wir deshalb die Software starten, die die 21 Millionen ins Leben rufen.
Natürlich kommen manche Leute - ich glaube, die meisten - auf Umwegen zum Bitcoin. Du denkst, dass es sich um einen spekulativen Vermögenswert handelt, etwas, das existiert, um mehr Dollar zu verdienen, d. h. um mehr Papiergeld zu verdienen. Oder du entdeckst ihn über Online-Glücksspiele oder andere Wege, und auf diese Weise kommen sie zu ihren ersten Sätzen. Aber selbst wenn du auf Umwegen zu Bitcoin kommst, selbst wenn Bitcoin vor deiner Haustür ankommt, ohne dass du verstehst, womit du es zu tun hast, musst du lernen, Bitcoin selbstbestimmt zu nutzen, oder du wirst es nicht schaffen.
Bitcoin auf eine selbstsouveräne Art und Weise zu nutzen, bedeutet, dass du die Memes von Bitcoin absorbieren musst. Zum Beispiel musst du die „21 Millionen" übernehmen und ihnen zustimmen, sonst hast du keinen Bitcoin, sondern einen Shitcoin in den Händen. Bitcoin am Laufen zu halten bedeutet, Bitcoin auszuleben, was wiederum bedeutet, seine eigenen Schlüssel zu besitzen, seinen eigenen Knoten zu betreiben und den zentralen Konsensparametern zuzustimmen, die Bitcoin zu Bitcoin machen.
Mit der Zeit wird ein horizontaler Meme-Transfer stattfinden. Bitcoin wird auf dich abfärben. Du wirst nicht nur den Ideen ausgesetzt sein, die in Bitcoin eingebettet sind; nein, du wirst ein Teil davon sein und das Meme leben, indem du die Satoshi Tag für Tag und Block für Block hältst.
Oder du wirst es nicht. Wenn du mit den Ideen, die in den Konsensparametern von Bitcoin eingebettet sind, nicht einverstanden sind, hast du zwei Möglichkeiten: Du kannst dich abspalten oder unter dem Bitcoin Derangement Syndrom leiden. Man kann sich natürlich auch an die Umwelt anpassen und in Symbiose mit ihr leben, was bedeutet, sich mit dem in Bitcoin eingebetteten memetischen Material zu arrangieren - es zu akzeptieren und ihm langsam zuzustimmen.
Wenn man die zuvor skizzierte ökologische Sichtweise anwendet, bilden Bitcoin und die Bitcoiner selbst den Organismus-Umwelt und beeinflussen sich gegenseitig in 10-Minuten-Intervallen. Das Knifflige daran ist, dass Bitcoin sowohl Organismus als auch Umwelt ist, genau wie wir selbst. Das Bitcoin-Meme lebt in unseren Gehirnen und unsere Vorstellung davon, was Bitcoin ist - und was es sein sollte - ändert sich mit der Zeit. Die ökonomische Erweiterung von uns - unsere Sats - leben in der Umgebung, die Bitcoin ist, eine Umgebung, die wir individuell und kollektiv hervorbringen.
Wir formen unsere Werkzeuge, und unsere Werkzeuge formen uns. Und wir benutzen unsere Werkzeuge, um unsere Umwelt zu formen, die natürlich auch uns formt. Kultur ist das Ergebnis dieser gegenseitigen Beeinflussung, und was ist Kultur anderes als eine Vielzahl von Memen?
Bei Bitcoin haben wir es mit einem unglaublichen meinungsbildenden Werkzeug zu tun, das eng mit uns verwoben ist. Ein Werkzeug, das ein Umfeld schafft, das lächerlich schwer zu ändern ist. Ich würde sogar so weit gehen zu sagen, dass einige Aspekte dieser seltsamen Meme-Werkzeug-Organismus-Umwelt-Schleife unmöglich zu ändern sind, da dies die Identität von Bitcoin und Bitcoinern gleichermaßen zerstören würde.
Für mich wird Bitcoin immer durch 21ismus definiert werden, auch wenn ich der letzte Mensch wäre, der an dieses Meme glauben würde. Anstelle dessen würde ich lieber auf dem Hügel von 21 Millionen sterben - allein und in Armut, mit dem Node in der Hand und zwölf Worten in meinem Kopf - als einer Erhöhung des Bitcoin-Angebots um 1 % zuzustimmen. (Buchvorschlag: Mandibles)
Es gibt diejenigen, die diese unveränderliche Umgebung akzeptieren, und diejenigen, die sie ablehnen, was natürlich zu einer Spaltung der Kultur führt.
Kulturelle Spaltungen
Wir erleben zweifelsohne eine Art Kulturkrieg. Links gegen Rechts, Rot gegen Schwarz, Based gegen Woke, Blue Bird gegen Purple Bird und Furries gegen normale Menschen. Es ist schwer, die Bruchlinien auszumachen, die diesem Krieg zugrunde liegen. Einige glauben, dass es auf Individualismus gegen Kollektivismus hinausläuft. Andere sehen es als Kapitalismus vs. Marxismus, selbstregulierende Ordnung vs. zentrale Planung. Wieder andere spekulieren, dass dieses Chaos mit dem Rückgang des religiösen Glaubens zusammenhängt, der eine Folge der nietzscheanischen Ermordung Gottes ist.
Alle diese Gründe mögen zutreffend oder teilweise zutreffend sein, aber für mich als Bitcoiner - als jemand, der die Graphen des "WTF geschah 1971" viele Male bestaunt hat - ist es schwer, etwas anderes als den Notstand des Fiat-Geldes als den Hauptgrund für das Chaos, das wir erleben, zu benennen. Für mich scheint es offensichtlich, dass diese verrückten Zeiten ein Ergebnis des Fiat-Geldsystems und der wirtschaftlichen sowie memetischen Konsequenzen sind, die es mit sich bringt. Es ist ein System, das völlig von der Realität abgekoppelt ist, ein künstliches und hochpolitisches Umfeld, das, ob wir es erkennen oder nicht, das wirtschaftliche Betriebssystem unserer Welt ist. Für mich lässt sich die Bruchlinie der Gesellschaft am besten als „Bitcoin vs. Fiat" zusammenfassen.
Seit 50 Jahren leben wir die Idee des Fiat-Geldes aus. Das Meme, dass die Art des Basisgeldes keine Rolle spielt, die hartnäckige Überzeugung, dass „wir es uns selbst schulden". Wir scheinen zu glauben, dass unsere kollektive Zukunft ein magischer goldener Topf ist - scheinbar ohne Boden -, aus dem wir uns immer und immer wieder etwas leihen können.
Ich glaube, dass wir uns in der Endphase des großen Fiat-Experiments befinden. Einmal mehr haben die arroganten Könige dieser Welt beschlossen, Gott zu spielen und sich in Kräfte einzumischen, die größer sind als sie, größer als wir. Wieder einmal müssen wir feststellen, dass das Drucken von Geld keinen wirklichen Wert schafft. Einmal mehr wird sich die Gesellschaft wandeln oder ganz zusammenbrechen, wie es in Ägypten, Rom und in vielen anderen Kulturen vor der unseren geschah. Und einmal mehr wird sich die Natur durchsetzen, indem sie Verwüstung anrichtet und alles ausrottet, was nicht mit ihr übereinstimmt. Seien es Ideen oder anderes.
„Als es nun an Geld gebrach im Lande Ägypten und in Kanaan, kamen alle Ägypter zu Josef und sprachen: Schaffe uns Brot! Warum lässt du uns vor dir sterben? Denn das Geld ist zu Ende."\ \ Mose 47:15
Diesmal ist das Fiat-Experiment jedoch nicht lokal begrenzt. Es ist nicht das Geld eines einzelnen Landes, das versagt, sondern das Meme des Fiat-Geldes selbst.
Geld drucken vs. das Geld in Ordnung bringen
Die Erkenntnis der Bedeutung des Geldes sowie der moralischen und kulturellen Implikationen der Natur des Geldes - und der Ethik der Geldproduktion - hat mein Weltbild unwiderruflich verändert. Als ich erkannte, dass Gelddrucken nichts anderes als eine Umverteilung von Reichtum ist und dass eine zentral geplante Umverteilung von Reichtum eine unmögliche Aufgabe ist - nicht nur rechnerisch, sondern auch moralisch -, dämmerte mir, dass Konfiszierung durch Inflation und andere Formen der unfreiwilligen Umverteilung nichts anderes ist als Diebstahl auf Umwegen. Das Fiat-System ist ein System der Sklaverei, und nein, das ist keine Übertreibung.
Aber hier ist die gute Nachricht: Bitcoin schafft hier Abhilfe.

Das ist unsere Meme-Welt, alle anderen leben nur darin.
Es gibt eine bestimmte Ethik, die in Bitcoin eingebettet ist, und es ist diese Ethik, die den Grundstein für die Meme bildet, die wir entstehen und sich verbreiten sehen. Wenn ich es in einem Satz zusammenfassen müsste, dann wäre es dieser: „Du sollst nicht stehlen." Wenn ich es in einer Zahl zusammenfassen müsste, dann wäre es natürlich 21 Millionen.
Die Motivation hinter der Erschaffung von Bitcoin ist zweifelsohne politisch, wie „Kanzlerin am Rande der zweiten Bankenrettung" und verschiedene Kommentare von Satoshi zeigen. So stimmte Satoshi zwar der Aussage zu, dass „sie in der Kryptographie keine Lösung für politische Probleme finden werden", aber er erwähnte auch, dass „wir eine wichtige Schlacht im Wettrüsten gewinnen und ein neues Territorium der Freiheit gewinnen können". Man beachte die Worte, die in dieser Aussage verwendet werden: ein Gebiet (Umfeld) der Freiheit (im Gegensatz zur Sklaverei).
Ich würde argumentieren, dass „eine große Schlacht gewinnen" eine Untertreibung ist, und ich würde auch argumentieren, dass die ursprüngliche Behauptung falsch ist, aber ich werde darauf zurückkommen.
Doch auch ohne diese Kommentare, selbst wenn die in den Genesis-Block eingebettete Botschaft „ooga chaka ooga ooga ooga chaka" lauten würde, wäre Bitcoin immer noch politisch. Ja, das daraus resultierende System ist unpolitisch, genau wie der Sonnenaufgang unpolitisch ist, aber der Akt der Schaffung von bitcoin ist ein politischer Akt. Er ist eine Aussage, eine Manifestation bestimmter Ideen, von Qualitätsmemes.
Vergleiche die in Bitcoin eingebettete Ethik (festes Angebot, keine erzwungene Umverteilung, kein kostenloses Mittagessen, keine Rettungsaktionen) mit der Ethik des Fiat-Geldes (endloses Angebot, zentral geplante Umverteilung, Rettungsaktionen für Freunde, alles ist erfunden) - oder, noch drastischer, mit der „Ethik" der Shitcoins, die nur Fiat-Geld auf Steroiden ist (jeder kann sein eigenes Geld drucken, nichts ist wichtig, Rugpulls sind lustig und Dickbutts sind im Grunde die Mona Lisa).
Ist es eine Überraschung, dass die Kultur rund um diese Phänomene so unterschiedlich ist? Oder ist „du wirst nichts besitzen und du wirst glücklich sein" einfach eine Folge des Mems, das Fiat-Geld ist? Ist der kulturelle Unterschied zwischen Bitcoinern und Shitcoinern ein natürliches Ergebnis der Meme, die in den verschiedenen Organismus-Umgebungen eingebettet sind und von diesen hervorgebracht werden?
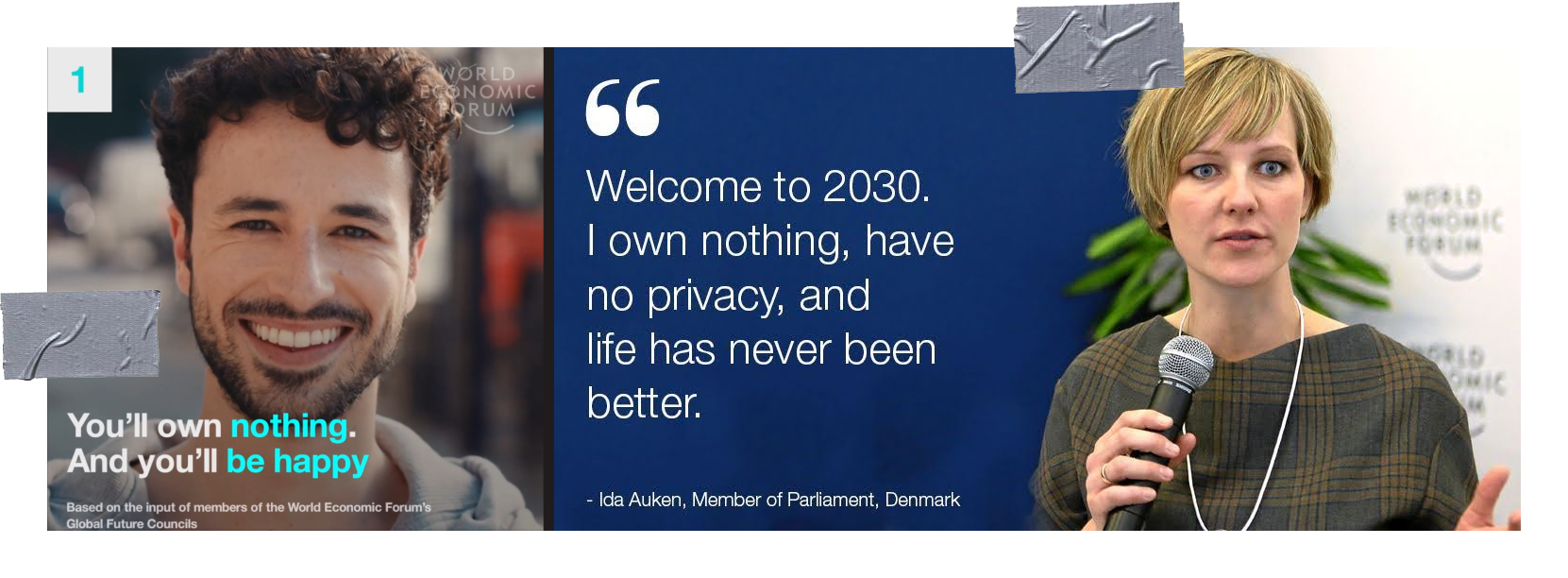
Im Klartext bedeutet das Meme des Fiat-Geldes - die Idee, dass wir Geld aus dem Nichts erschaffen können und sollten - einfach zu sagen: „Ich weiß besser als der Markt, wie man Geld verteilt", was bedeutet, dass ich besser als alle anderen weiß, was gut und was schlecht ist, was wertvoll ist und was nicht, was notwendig und was überflüssig ist.
Die Frage, die das Fiat-System beantwortet, ist die folgende: Wer darf Geld fälschen und wie viel? Und wer darf Zugang zu Geld haben, und wer nicht? Die Antwort ist politisch und wird mit Gewalt durchgesetzt.
Das Bitcoin-System beantwortet dieselben Fragen, und die Antworten sind ebenso einfach wie ethisch: Niemand darf Geld fälschen, und jeder kann darauf zugreifen. Keine Ausnahmen.
Dies sind zwei sehr unterschiedliche Ideen, zwei sehr unterschiedliche Memes. Die eine wird im Fiat-System umgesetzt, die andere im Bitcoin-System. Das eine bricht aus den Nähten, das andere tuckert vor sich hin und wächst wirtschaftlich, rechnerisch und memetisch - alle 10 Minuten.
Bitcoin vs. Gold
Wenn es darum geht, die Grundursache vieler unserer Übel zu identifizieren, hatten die Goldanhänger (größtenteils) die richtige Idee. Aber sie hatten keine Möglichkeit, ihre Ideen auf sinnvolle und effektive Weise umzusetzen, die in der vernetzten Welt des 21. Das Meme des „gesunden Geldes" ist das richtige Mem, aber ohne eine Möglichkeit, dieses Meme effizient umzusetzen, hat das Meme keine Möglichkeit, sich in der Bevölkerung zu verbreiten.
So sieht es aus, liebe Goldfresser: Wir werden nicht zu einem Goldstandard zurückkehren. Gold hat in der Vergangenheit versagt, und es würde auch in der Zukunft versagen. Die Nützlichkeit des „Goldstandard"- Memes ist zu einem Ende gekommen. Das Überbleibsel seiner glorreichen Vergangenheit wird nur noch in der Linguistik zu finden sein.
„Warum", fragst du dich? Nun, zunächst einmal verbietet der physische Körper des Goldes die Teleportation, d. h. die elektronische Übertragung von Gold. Er verbietet die Unsichtbarkeit, d. h. die plausible Abstreitbarkeit des Besitzes. Bitcoin kann sofort teleportiert und perfekt versteckt werden. Man kann ihn im Kopf behalten, und niemand kann wissen, ob man Bitcoin tatsächlich besitzt oder nicht. Gold wird allein aus logistischen Gründen immer in Tresoren zentralisiert sein. Bitcoin muss das nicht sein. Gold wird sich immer mit einer bestimmten Rate aufblähen, da eine unbekannte Menge noch unter der Erde (und im Weltraum) liegt. Die Menge, die sich über der Erde befindet, ist ebenfalls unbekannt, da der weltweite Goldvorrat nicht einfach überprüft werden kann.
Im Gegensatz dazu ist Bitcoin absolut knapp und perfekt überprüfbar. Alle 10 Minuten wird der Gesamtvorrat an Bitcoin geprüft. Alle 10 Minuten wird der Emissionsplan überprüft. Alle 10 Minuten werden Milliarden von Sats endgültig und elektronisch, d.h. mit Lichtgeschwindigkeit, abgerechnet. Eine echte, physische Abrechnung. Global und sofort, ohne große Kosten oder Reibungsverluste. Alle 10 Minuten.

Das Gold-Meme wird sich noch eine Weile halten, und das ist auch gut so. Die Menschen sind nostalgisch, besonders wenn sie in ihren Gewohnheiten verhaftet sind. Wie bei wissenschaftlichen Revolutionen wird sich die monetäre Revolution, die derzeit im Gange ist, wahrscheinlich langsam verbreiten: eine Beerdigung nach der anderen.
Ich glaube jedoch, dass Bitcoin die Macht hat, die Köpfe und Herzen der Menschen sehr schnell zu gewinnen, wenn diese Köpfe offen oder kulturell angepasst genug sind; oder wenn die Veränderung in ihrem Umfeld drastisch genug ist.
Politik vs. Kultur
Kehren wir zu der Behauptung zurück, dass "du in der Kryptographie keine Lösung für politische Probleme finden werden". Ich habe bereits erwähnt, dass ich dem nicht zustimme, und hier ist der Grund. Politik ist der Kultur nachgelagert, und Kryptographie im Allgemeinen (und Bitcoin im Besonderen) verändert die Kultur.
Das sollte jedem außer dem blindesten Beobachter des Bitcoin-Bereichs sonnenklar sein. Die Kultur rund um Bitcoin ist durchdrungen von Verantwortung und Selbsteigentum („besitze deine eigenen Schlüssel" & „nicht deine Schlüssel, nicht dein Bitcoin"), Verifizierung und Schlussfolgerungen aus ersten Prinzipien ("vertraue nicht, verifiziere"), langfristigem Denken und Sparen für die Zukunft ("bleibe bescheiden, staple Sats"), sowie einem Fokus auf harte Arbeit, Integrität, Wahrheit und sichtbare Ergebnisse ("Proof-of-work, der Arbeitsnachweis").
Satoshi erkannte in wahrer Cypherpunk-Manier, dass Memes implementiert werden müssen, um sich möglichst effizient zu verbreiten, weshalb er sich hinsetzte und den Code schrieb. Es war auch der erste Test für die Tauglichkeit seiner Ideen, wie er in einem seiner vielen Forenbeiträge erwähnte: „Ich musste den ganzen Code schreiben, bevor ich mich selbst davon überzeugen konnte, dass ich jedes Problem lösen kann, und dann habe ich das Whitepaper geschrieben."
Das ist der Arbeitsnachweis, genau da. Das ist Anti-Fiat. Nicht nur darüber reden, sondern es auch tun. Mit gutem Beispiel vorangehen. Nicht nur über die Ideen spekulieren, die man im Kopf hat, die Memes, die man in der Welt verbreitet sehen möchte, sondern sie auch umsetzen. Das heißt, sie an der Realität zu messen.
„Lass deine Memes keine Träume sein."
Satoshi (paraphrasiert)
Ist es eine Überraschung, dass sich Bitcoin in den Bereichen „gesunde Ernährung", „gesunde Landwirtschaft", „freie Meinungsäußerung und Menschenrechte ausbreitet? Dass Bitcoin schnell und einfach von Menschen verstanden wird, die buchstäblich nahe am Boden sind, verbunden mit der grundlegenden Realität der Dinge? Ist es eine Überraschung, dass Bitcoin von denjenigen genutzt und verstanden wird, die es am meisten brauchen? Von denjenigen, die in Ländern leben, in denen das Geld versagt? Von denjenigen, die vom Fiat-System abgelehnt werden?
Das sollte keine Überraschung sein. Einige Kulturen haben eine natürliche Überschneidung mit der Bitcoin-Kultur, und es sind diese Kulturen, die Bitcoin zuerst annehmen werden. Frühe Beispiele sind die Cypherpunk-Kultur sowie die Kulturen rund um die österreichische Wirtschaft, den Libertarismus und das muslimische Finanzwesen. Wenn diese Kulturen Bitcoin annehmen, wird Bitcoin seinerseits diese Kulturen annehmen und dich beeinflussen. Ein für beide Seiten vorteilhafter Einfluss, wie er für alles, was langfristig überlebt, erforderlich ist, und wie er für die Symbiose, die die Natur darstellt, Standard ist. Der Organismus und das Umfeld, das durch die orangefarbene Münze und ihre Besitzer geschaffen wird, will überleben. Bitcoin: das egoistische Meme.
Natürlich gibt es auch Fiat-Meme. Es ist das, was unsere Kultur in den letzten 50 Jahren geprägt hat: „Fake it till you make it" und „YOLO" kommen mir in den Sinn, was interessanterweise die moderne Version der keynesianischen Idee ist, dass wir auf lange Sicht alle tot sind. Ist es verwunderlich, dass ein Umfeld, das durch falsches Geld geschaffen wurde, zu falschem Essen, falschen Körpern, falscher Gesundheit, falscher Medizin, falschen Beziehungen, falschen Experten und falschen Menschen führt?
Diejenigen, die an der Spitze der Fiat-Pyramide sitzen, sprechen von „nutzlosen Essern" und versuchen uns davon zu überzeugen, dass wir nichts besitzen müssen, aber trotzdem glücklich sein werden. Man muss sich über den Slogan wundern: „Du wirst nichts besitzen und du wirst glücklich sein".
„Du wirst ein glücklicher kleiner Sklave sein", heißt es in diesem Meme. Jemand hat beschlossen, dass Glück das ultimative Ziel ist, das es zu erreichen gilt, und du (und nur du) weißt, wie du es für dich erreichen können.

„Glück"
Als ob Glück das eigentliche Ziel wäre, das A und O, der Grund für unsere Existenz. Was ist mit dem Streben nach etwas Sinnvollem, etwas, das schwer ist, etwas, das Opfer erfordert, das Schmerz und Leid mit sich bringt?
\ „Jeder Mensch ist glücklich, bis das Glück plötzlich ein Ziel ist."
Oder was ist mit der Aussage von Lagarde, dass „wir glücklicher sein sollten, einen Arbeitsplatz zu haben, als dass unsere Ersparnisse geschützt sind?" Das ist Ausdruck eines bestimmten Memes, das sich in ihrem Kopf festgesetzt hat, des Mems, dass Arbeitsplatzsicherheit die meisten anderen Bedürfnisse übertrumpft und dass normale Menschen kein Vermögen anhäufen müssen. Schlimmer noch: Es suggeriert, dass es völlig in Ordnung ist, das zu stehlen, was normale Menschen durch fleißige Arbeit im Laufe ihres Lebens angespart haben.
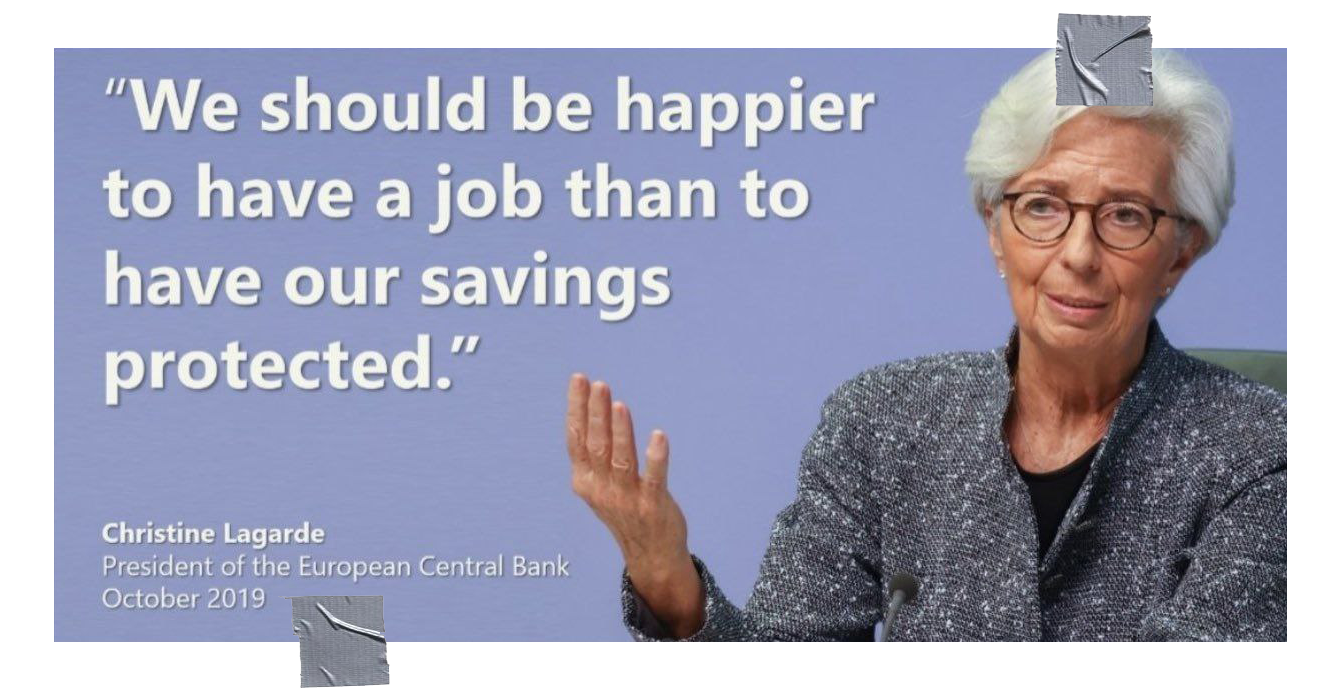
Wir sollte glücklicher sein einen Job zu haben als das unsere Erparnisse geschützt werden. Christine Largarde Präsidentin der ECB, Oktober 2019
Es gibt einen Grund, warum wir vom „Rattenrennen" oder dem „Hamsterrad" sprechen und warum dieser Teil unserer Kultur in Kunst und Film so stark kritisiert wird. Um Tyler Durden zu zitieren: „Die Werbung bringt uns dazu, Autos und Klamotten zu jagen, Jobs zu machen, die wir hassen, damit wir Scheiß kaufen können, den wir nicht brauchen. Wir sind die mittleren Kinder der Geschichte, Mann. Wir haben keinen Sinn und keinen Platz. Wir haben keinen Großen Krieg. Keine Weltwirtschaftskrise. Unser großer Krieg ist ein spiritueller Krieg... unsere große Depression ist unser Leben. Wir sind alle durch das Fernsehen in dem Glauben erzogen worden, dass wir eines Tages alle Millionäre, Filmgötter und Rockstars sein werden. Aber das werden wir nicht. Und wir lernen diese Tatsache langsam kennen. Und wir sind sehr, sehr wütend."
Ich glaube jedoch nicht, dass die Menschen wütend sind. Ich glaube, dass die meisten Menschen deprimiert und nihilistisch sind. Sie sehen keinen Ausweg, sie sind hoffnungslos und haben sich mit ihrer Position im System abgefunden - ob bewusst oder unbewusst.
Nichts zeigt die Plackerei des Fiat-Rattenrennens besser als der kurze Animationsfilm „Happiness", der eine visuelle Reise durch die unerbittliche Suche des Menschen nach Erfüllung in der modernen Welt darstellt. Er setzt in Bilder um, was viele Menschen nicht in Worte fassen können. Hilflosigkeit, Sucht, Hoffnungslosigkeit. Eine Krise des Selbst, eine Krise des Sinns. Das Fehlen einer hoffnungsvollen Vision für die Zukunft.
„Ehrlich gesagt, ist es ziemlich deprimierend", so ein 44-jähriger Arbeiter, der allein im Wald festsitzt. „Ich habe versucht, einen Gedanken zu formulieren, ihn auszudrücken, ohne zusammenzubrechen und zu weinen. Aber ich bin mir nicht sicher, ob ich ihn weitergeben kann, ohne zu weinen."
„Mein Problem, einer der Gründe, warum ich hierher kommen wollte, war also, dass ich versuchen wollte, über den neuen Aspekt meines Lebens nachzudenken. Mit anderen Worten: nach den Kindern."
„Ein Mensch kann eine Menge Dinge ertragen, für jemanden, den er liebt. Die gleichen Dinge nur für sich selbst zu ertragen, ist nicht so einfach. Ich bin Elektriker. Man könnte meinen, das sei nicht so schwer, aber es sind viele sich wiederholende Aufgaben. Ich weiß, dass jeder seine eigene Arbeit hat, ich weiß, dass das einfach der Lauf der Welt ist. Aber für mich ist der Gedanke, dass ich weitere 15 Jahre meines Lebens damit verbringen muss, auf die Wochenenden zu warten, einfach eine Qual. Einfach nur die banale Qual des Ganzen..."
Schau dir bei Möglichkeit diesen Clip an. Es ist eine Sache, über das Meme des Rattenrennens zu theoretisieren; es ist eine andere Sache, einem erwachsenen Mann zuzusehen, der weinend zusammenbricht, nachdem er über sein Leben, das System, in das er eingebettet ist, und die Zukunft, die dieses System für ihn bereithält, nachgedacht hat. Nachdem er sich die Tränen weggewischt hat, spekuliert er darüber, was der Grund für seine depressive Stimmung sein könnte: „An diesem Ort kenne ich die Regeln. Es ist das Leben außerhalb dieses Ortes, das mich zum Weinen bringt."
Das ist es, nicht wahr? Regeln und Regeländerungen. Wenn du jemanden zutiefst deprimieren wollen, änderst du die Regeln, und zwar häufig. Zwingen du sie, etwas Sinnloses zu tun. Ändere die Regeln willkürlich. Das ist es, was die Menschen wirklich demoralisiert: in einem System willkürlicher Regeländerungen gefangen zu sein. Keine Hoffnung auf Stabilität und kein Ausweg.
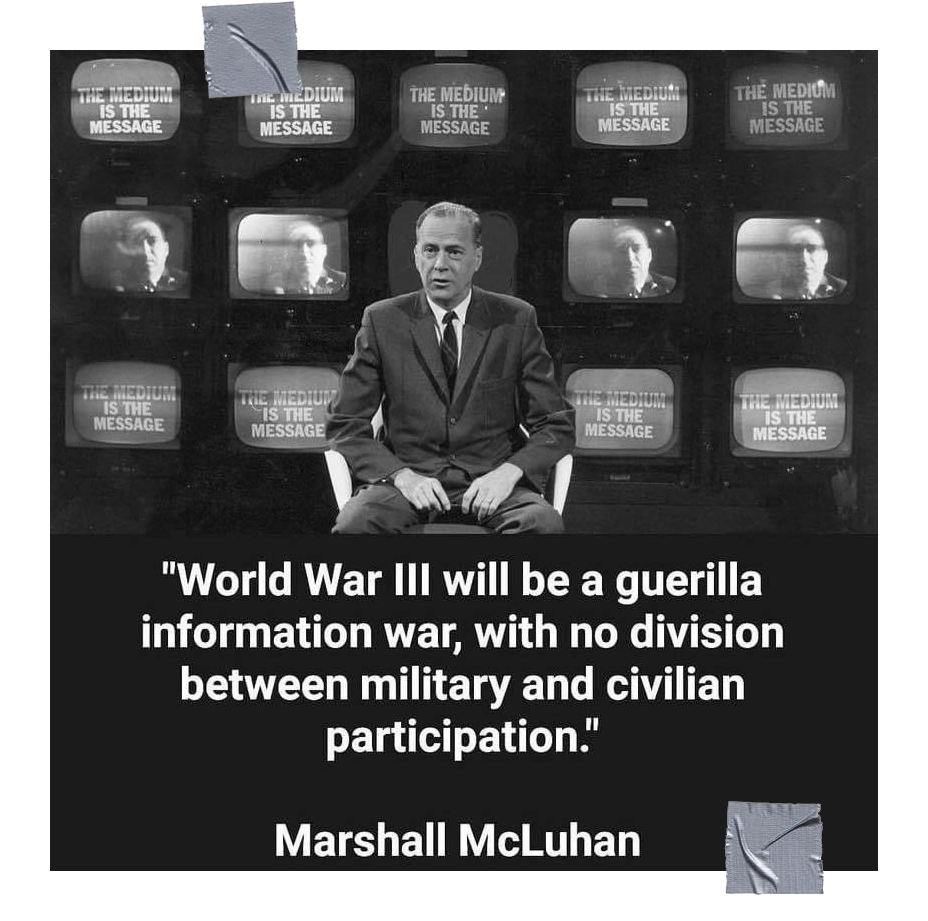
Der Dritte Weltkrieg wird ein Guerilla-Informationskrieg sein, bei dem es keine Trennung zwischen militärischer und ziviler Beteiligung gibt. - Marshall McLuhan
Das Meme ist die Nachricht.
"Weißt du, jetzt habe ich es endlich verstanden. Über den Unterschied zwischen einem echten Krieg und einem globalen Guerillakrieg. Denn was wir jetzt haben, ist kein konventioneller Krieg mit scharfen Waffen. Mit militärischer Ehre, militärischen Rängen, militärischer Aktivität... Das ist ein Kulturkrieg. Wir haben die Unruhen. Wir haben die Unordnung. Und jetzt weiß ich wirklich, wie das funktioniert. Wenn die Unruhen vorbei sind, kann man nicht mehr sagen: „Ich habe mit Stolz gedient. Es spielt keine Rolle, auf welcher Seite man steht. Denn die Unruhen sind ein Krieg gegen den Stolz. Es ist ein Krieg gegen die Moral der Menschen. Man kann dem Feind nicht als Gleicher gegenübertreten. Jeder lebt im Schatten. Es ist immer verdeckt. Es ist immer gefälscht. Er ist immer erfunden. Und es kann keine Geschichte darüber geschrieben werden, weil alles abgeschottet ist."\ \ Bruce Sterling
Für die Geldpolitik gibt es im Fiat-System keine Regeln. „Die Regeln sind erfunden, und die Punkte sind egal", um Drew Carey zu zitieren. Die Realität hat Regeln, und wenn ein Fiat-System erst einmal aus dem Ruder gelaufen ist, dann ist es die Realität, die die Konsequenzen zieht, nicht das Fiat-System selbst.
Das Fiat-System ist kaputt; sein Geld ist wertlos; seine Kultur ist deprimiert und hoffnungslos. Wenn die Politik der Kultur nachgelagert ist, ist es dann eine Überraschung, dass unsere Politik größtenteils eine Clownshow ist, die nur auf Äußerlichkeiten und kurzfristige Ziele ausgerichtet ist? Wo gibt es Hoffnung in der hoffnungslosen Welt des fiat everything? Kaputte Ideen führen zu kaputten Umgebungen, die wiederum zu kaputten Organismen führen. Ist der Mensch erst einmal kaputt, wird er nicht in der Lage sein, seine Umwelt auf eine für alle Seiten vorteilhafte Weise zu verändern. Ganz im Gegenteil. Er wird in einer Abwärtsspirale aus Verzweiflung und Zerstörung feststecken und versuchen, „um jeden Preis" zu tun, was nötig ist.
Ohne Bitcoin sind die Aussichten für unsere Zukunft düster. Ohne Bitcoin hast du zwei Möglichkeiten: die schwarze Pille des Pessimismus oder das Soma des Nihilismus.
Es gibt einen Grund, warum die Leute sagen, dass Bitcoin Hoffnung ist.
Schwarze Pille vs. Orange Pille
Bitcoin ist Hoffnung, weil die Regeln von Bitcoin bekannt und stabil sind. Das Bitcoin-System ist wahnsinnig zuverlässig, funktioniert wie ein Uhrwerk, mit Regeln, die bekannt und in Stein gemeißelt sind. Es ist eine Umgebung mit eisenharten Zwängen, die ohne Herrscher durchgesetzt werden.
Es ist nicht nur das Gegenteil des Fiat-Systems, sondern auch sein Gegengift. Es ist nicht nur ein Rettungsboot, in das jeder einsteigen kann, der in Not ist, sondern auch ein Heilmittel, das Sinn und Optimismus gibt, wo es vorher keinen gab.
Es ist leicht, depressiv zu werden, wenn man die Übel des Fiat-Systems erkannt hat. Viele Bitcoiner, die heute von Optimismus erfüllt sind, waren hoffnungslos und fatalistisch, bevor sie die orangefarbene Pille schluckten. Viele Menschen sind es immer noch, Lionel Shriver und die meisten Goldfresser eingeschlossen.
Aber man muss bereit sein. Man kann sich nur selbst eine orangefarbene Pille geben, wie man sagt. Niemand kann dir Bitcoin aufzwingen.
Du müsstest eine Erleuchtung haben, dieselbe Erleuchtung wie unser 44-jähriger Elektriker im Wald, der über sein Leben nachdenkt. Kurz nach seinem Zusammenbruch und seinem Monolog darüber, dass er im Rattenrennen feststeckt, kommt er zu einer plötzlichen Erkenntnis: „Ich muss etwas ändern. Es ist nicht die Welt, die sich ändern muss. Es bin ich, der sich ändern muss. Es ist meine Einstellung zum Leben."
Ja. Was für ein Chad.
Das ist buchstäblich die Funktionsweise von Bitcoin.
Fiat Denkweise vs. Bitcoin Denkweise
\ Das Fiat-System wird nicht einfach verschwinden, und es wird auch nicht still und leise verschwinden. Zu viele Menschen sind immer noch mit dem Gedanken an leicht verdientes Geld infiziert, arbeiten in Scheißjobs und führen ein Fiat-Leben. Der Tod des Fiat-Organismus ist jedoch unausweichlich. Er ist selbstzerstörerisch, und wie alle Tiere, die in die Enge getrieben werden und am Rande des Todes stehen, wird er in einem letzten Versuch, das Unvermeidliche zu verhindern, um sich schlagen.

Piggies von artdesignbysf
„Unser großer Krieg ist ein spiritueller Krieg", wie Tyler Durden es so treffend formulierte. Und wir sind mittendrin in diesem Krieg.
Mit jedem Tag wird es offensichtlicher, dass dies ein geistiger Krieg ist. Ein Zusammenprall von Ideen, ein Kampf der unterschiedlichen Weltanschauungen.
Selbst der letzte Boss von Bitcoin, Augustin Carstens, weiß, dass dies ein Krieg ist. Warum sonst würde er, die Verkörperung des Fiat-Standards, im Fernsehen auftreten und Folgendes sagen?
„Vor ein paar Jahren wurden Kryptowährungen als Alternative zu Papiergeld dargestellt. Ich denke, diese Schlacht ist gewonnen. Eine Technologie macht noch kein vertrauenswürdiges Geld."
Augustin Carstens
Wenn wir uns nicht in einem memetischen Krieg befänden, warum wäre es dann notwendig zu erklären, dass eine Schlacht gewonnen wurde?
Wenn wir uns nicht mitten in einem spirituellen Krieg befinden würden, warum würde Christine Lagarde, eine Person, die wegen Fahrlässigkeit und Missbrauchs öffentlicher Gelder verurteilt wurde - eine Person, die jetzt Präsidentin der Europäischen Zentralbank ist - öffentlich erklären, dass wir Bitcoin auf globaler Ebene regulieren müssen, denn „wenn es einen Ausweg gibt, wird dieser Ausweg genutzt werden?"
Warum würde Stephen Lynch behaupten, dass Bitcoin „auf Null gehen wird, wenn wir ein CBDC entwickeln, das den vollen Glauben und Kredit der Vereinigten Staaten hinter sich hat?"
Warum würde Neel Kashkari, verrückt wie er ist, vor eine Kamera treten, um das Mem zu verbreiten, dass „es unendlich viel Bargeld in der Federal Reserve gibt", in der Hoffnung, dass diese Aussage das Vertrauen in das zusammenbrechende Fiat-System stärken würde?

Es ist fast unmöglich, sich diese Interviews anzusehen, ohne den Kopf zu schütteln. Glauben diese Menschen wirklich, was sie sagen? Ist es Böswilligkeit oder ist es Unwissenheit? Oder ist es einfach ein Auswuchs der verzerrten Weltsicht des Fiat-Verstandes? Sind diese Menschen nicht mehr zu retten, oder könnte Bitcoin sie sogar demütigen und sie auf den Pfad der Verantwortung und der Finanzdisziplin bringen?
Wie auch immer die Antwort lauten mag, die bloße Existenz von Bitcoin ist eine Beleidigung für ihr Denken, oder für jedes Fiat-Denken, was das betrifft. Bitcoin setzt die Idee außer Kraft, dass Geld vom Staat geschaffen werden muss. Seine Architektur sagt: „Jeder sollte Zugang zum Geldsystem haben". Sein Design sagt: „Wir sehen, was ihr getan habt, Fiat-Leute, und wir werden dem ein Ende setzen."
„Die Existenz von Bitcoin ist eine Beleidigung für den Fiat-Verstand."
\ Es ist ironisch, dass das, was die meisten Fiat-Leute zuerst sehen, die Schlachtrufe der Bitcoiner sind, die „HODL!" schreien und „wir werden euch obsolet machen" von den Dächern schreien. Du übersiehst die tiefere Wahrheit dieser Memes, die Tatsache, dass diese Meme der tiefen Überzeugung entspringen, dass ein mathematisch und thermodynamisch gesundes System einem politischen System vorzuziehen ist. Sie hören weder das Brummen der ASICs, noch achten sie auf die gültigen Blöcke, die unaufhörlich eintreffen. Alle 10 Minuten wird leise geflüstert: „Du sollst nicht stehlen."
Das laute und prahlerische Oberflächenphänomen lässt sich leicht ins Lächerliche ziehen und abtun. Der zutiefst technische, wirtschaftliche und spieltheoretische Organismus, der die 21 Millionen zustande bringt, nicht so sehr. Beide sind im Wachstum begriffen. Beide sind miteinander verwoben. Das eine kann ohne das andere nicht existieren.
Fiat-Selbst vs. Bitcoin-Selbst
\ Beim ersten Kontakt wird der Bitcoin von den meisten abgetan. In einer Welt, die vom Fiat-Standard beherrscht wird, sind die meisten Menschen nicht in der Lage, die orangefarbene Münze zu verstehen, wenn sie zum ersten Mal über sie stolpern. Ich denke, man kann mit Sicherheit sagen, dass die meisten Bitcoiner es nicht sofort „verstanden" haben. Ich habe es anfangs sicherlich nicht verstanden.
Die Reise vieler Bitcoiner lässt sich wie folgt zusammenfassen:
- Was zum Teufel ist das?
- Was zum Teufel ist das?
- Was zur Hölle?
- Die Scheiße?
- Scheiße...
- All in.
Der Prozess des Verstehens und der Annahme von Bitcoin ist der Prozess des Verlassens deines Fiat-Selbst hinter sich. Man muss die Fiat-Memes aus dem Kopf bekommen und die Bitcoin-Memes hineinlassen. Du musst dein Fiat-Selbst ausbrennen und dein Bitcoin-Selbst aufbauen. Tag für Tag, Aktion für Aktion, Block für Block.
Indem du am System der Fiat-Schuldensklaverei teilnimmst, verstärkst du das Meme der sofortigen Befriedigung, der Diskontierung der Zukunft für die Gegenwart, des falschen Geldes und des kurzfristigen Denkens. Indem du am Bitcoin-System teilnimmst, stärkst du das Mem des gesunden Geldes, des unelastischen Angebots, des langfristigen Denkens, der Verantwortung und der unveräußerlichen Eigentumsrechte.
„Man kann die Revolution nicht kaufen. Man kann die Revolution nicht machen. Du kannst nur die Revolution sein. Sie ist in deinem Geist, oder sie ist nirgendwo." - Ursula K. Le Guin
Verstehe mich nicht falsch. Es ist nichts falsch daran, in den Fiat-Minen zu arbeiten und bescheiden Sats zu stapeln. Es ist eines der wichtigsten Dinge, die du tun kannst. Das Stapeln von Sats gibt dir Freiheit, Kontrolle und Selbstständigkeit. Es ermöglicht dir, sich in eine Position der Stabilität und Stärke zu manövrieren, und ehe du dich versiehst, wird der einfache Akt des demütigen Stapelns und der Liebe zu deinem zukünftigen dich selbst verändern.
Der wahre Kampf ist ein persönlicher Kampf. Den Drang zu unterdrücken, etwas umsonst haben zu wollen. Die Gewohnheit der sofortigen Befriedigung aufzugeben und eine Kultur des langfristigen Denkens aufzubauen. Ablehnung von impulsiven Ausgaben, Akzeptanz von Opfern und Einschränkungen.
Die Beziehung zwischen Ihnen und der Welt ist transaktional, wie John Dewey uns lehrte. Nicht nur unsere physischen Körper sind an unsere physische Umgebung gebunden, sondern wir sind auch über die ebenso reale wirtschaftliche Umgebung, an der wir uns beteiligen, miteinander verbunden. Und mit jedem Dollar, den wir ausgeben, und jedem Satoshi, den wir sparen, erschaffen wir unsere Zukunft.
Es gibt eine Weggabelung. Das Schild auf der einen Seite sagt: „Du wirst nichts besitzen und du wirst glücklich sein". Das Schild auf der anderen Seite sagt: „Du wirst Bitcoin besitzen und du wirst die beste Version deiner selbst sein."

Die Wahl liegt bei dir.
Bitcoin hat die Macht, die beste Version von sich selbst hervorzubringen, weil die Anreize von Bitcoin auf gegenseitige Verbesserung ausgerichtet sind. Auf individueller Ebene erfordert der Besitz von Bitcoin eine Änderung der Zeitpräferenz und der Verantwortung. Der Besitz impliziert, dass man seine eigenen Schlüssel besitzt. Wenn du das nicht tun, besitzts du keine Bitcoin, sondern Schuldscheine. Es bedeutet auch, dass du deinen eigenen Knotenpunkt betreiben, um zu überprüfen, ob du tatsächlich Bitcoin besitzen. Wenn man das nicht tut, vertraut man auf das Wort eines anderen, verlässt sich auf seine Sicht von Bitcoin, seine Weltsicht und darauf, dass er einen nicht anlügt.
Darüber hinaus bedeutet der fortgesetzte Besitz von Bitcoin, dass man die Verantwortung übernimmt, einen Wert für die Gesellschaft zu schaffen. Geld tut nichts anderes, als zu zirkulieren, also musst etwas leisten, das andere Menschen als wertvoll empfinden. Wenn du das nicht tust, wirst du bald keine Bitcoin mehr haben. Die Natur wird dich dazu zwingen, dich von deinen Sats zu trennen, denn jeder - auch du - muss essen.
„Beschäftige dich mit dem Sinn des Lebens, wirf leere Hoffnungen beiseite, engagiere dich für deine eigene Rettung - wenn du dich überhaupt um dich selbst kümmerst - und tue es, solange du kannst."\ \ Marcus Aurelius
Der Bitcoin-Weg ist kein einfacher Weg, aber ein erfüllender. Er ist erfüllend, weil du die Regeln kennst, du kennst die Konsequenzen, und du hast die Verantwortung. Es ist ein Weg, der es dir erlaubt, dein Leben so zu gestalten, wie du es für richtig hältst, aber du musstes auch selbst gestalten. Es ist ein Weg, der es dir ermöglicht, sich vor Übergriffen und Diebstahl zu schützen, und der langfristige Sicherheit und Stabilität bietet. Aber du musst ihn gehen. Du musst mitmachen. Du musst ihn ausleben.
Du musst dein Fiat-Selbst ausbrennen und die einfachen Antworten, die Abkürzungen und den Scheinwert hinter dir lassen. Du musst etwas Reales anbieten, jemand Reales sein und im Falle des Scheiterns die realen Konsequenzen tragen.
Die Grenze zwischen Gut und Böse verläuft nicht nur in jedermanns Herzen, sondern auch die Grenze zwischen Fiat und Bitcoin verläuft ebenfalls in jedermanns Herzen. Es geht nicht um „wir gegen sie". Es geht um unser Fiat-Selbst gegen unser Bitcoin-Selbst. Persönliche Verantwortung vs. vorsätzliche Ignoranz. Systemische Fragilität vs. langfristige Stabilität. Mit jeder Handlung triffst du eine Entscheidung, und du hast keine andere Wahl als zu handeln.
Es gibt eine Weggabelung, und jeder Einzelne von uns muss sich entscheiden, welchen Weg er einschlagen will. Den scheinbar bequemen Weg, den die Machthaber vorgeben, oder den Bitcoin-Weg: hart, steinig, mit Höhen und Tiefen, ohne Sicherheitsnetze und ohne Rettungsaktionen. Es ist kein einfacher Weg, aber es ist ein schöner Weg. Ein Weg, der Geduld, Verantwortung und Disziplin lehrt. Ein Weg, der dich demütig macht. Ein sinnvoller Weg. Ein Weg, den zu gehen sich lohnt.
Früher war es ein einsamer Weg, aber das ist er nicht mehr. Früher war es ein verrückter Weg. Heute ist der Weg zu mehr Freiheit der verrückte Weg. Es ist ein langer Weg, ein täglicher Kampf. Und niemand außer dir kann diesen Weg gehen. Ich würde dir gerne sagen, dass ich dich auf dem Gipfel treffe, aber ich fürchte, es gibt keinen Gipfel. Ich treffe dich stattdessen auf dem Weg.
Gigi ist ein professioneller Shitposter und Meme-Kenner. Er ist vor kurzem aus der woken Höllenlandschaft der Vogel-App in das lila gelobte Land des Straußen-Protokolls umgezogen. Wenn er nicht gerade Shitposting betreibt, ist er meistens damit beschäftigt, ein Bitcoin-Genießer zu sein und seine Pflaumen im Glanz der orangefarbenen Münze zu baden. Du kannst ihn herbeirufen, indem du seinem npub in den Kartenschlitz eines stillgelegten Geldautomaten flüsterst:
npub1dergggklka99wwrs92yz8wdjs952h2ux2ha2ed598ngwu9w7a6fsh9xzpc
-
 @ d34e832d:383f78d0
2025-04-25 23:20:48
@ d34e832d:383f78d0
2025-04-25 23:20:48As computing needs evolve toward speed, reliability, and efficiency, understanding the landscape of storage technologies becomes crucial for system builders, IT professionals, and performance enthusiasts. This idea compares traditional Hard Disk Drives (HDDs) with various Solid-State Drive (SSD) technologies including SATA SSDs, mSATA, M.2 SATA, and M.2 NVMe. It explores differences in form factors, interfaces, memory types, and generational performance to empower informed decisions on selecting optimal storage.
1. Storage Device Overview
1.1 HDDs – Hard Disk Drives
- Mechanism: Mechanical platters + spinning disk.
- Speed: ~80–160 MB/s.
- Cost: Low cost per GB.
- Durability: Susceptible to shock; moving parts prone to wear.
- Use Case: Mass storage, backups, archival.
1.2 SSDs – Solid State Drives
- Mechanism: Flash memory (NAND-based); no moving parts.
- Speed: SATA SSDs (~550 MB/s), NVMe SSDs (>7,000 MB/s).
- Durability: High resistance to shock and temperature.
- Use Case: Operating systems, apps, high-speed data transfer.
2. Form Factors
| Form Factor | Dimensions | Common Usage | |------------------|------------------------|--------------------------------------------| | 2.5-inch | 100mm x 69.85mm x 7mm | Laptops, desktops (SATA interface) | | 3.5-inch | 146mm x 101.6mm x 26mm | Desktops/servers (HDD only) | | mSATA | 50.8mm x 29.85mm | Legacy ultrabooks, embedded systems | | M.2 | 22mm wide, lengths vary (2242, 2260, 2280, 22110) | Modern laptops, desktops, NUCs |
Note: mSATA is being phased out in favor of the more versatile M.2 standard.
3. Interfaces & Protocols
3.1 SATA (Serial ATA)
- Max Speed: ~550 MB/s (SATA III).
- Latency: Higher.
- Protocol: AHCI.
- Compatibility: Broad support, backward compatible.
3.2 NVMe (Non-Volatile Memory Express)
- Max Speed:
- Gen 3: ~3,500 MB/s
- Gen 4: ~7,000 MB/s
- Gen 5: ~14,000 MB/s
- Latency: Very low.
- Protocol: NVMe (optimized for NAND flash).
- Interface: PCIe lanes (usually via M.2 slot).
NVMe significantly outperforms SATA due to reduced overhead and direct PCIe access.
4. Key Slot & Compatibility (M.2 Drives)
| Drive Type | Key | Interface | Typical Use | |------------------|----------------|---------------|-----------------------| | M.2 SATA | B+M key | SATA | Budget laptops/desktops | | M.2 NVMe (PCIe) | M key only | PCIe Gen 3–5 | Performance PCs/gaming |
⚠️ Important: Not all M.2 slots support NVMe. Check motherboard specs for PCIe compatibility.
5. SSD NAND Memory Types
| Type | Bits/Cell | Speed | Endurance | Cost | Use Case | |---------|---------------|-----------|---------------|----------|--------------------------------| | SLC | 1 | ⭐⭐⭐⭐ | ⭐⭐⭐⭐ | $$$$ | Enterprise caching | | MLC | 2 | ⭐⭐⭐ | ⭐⭐⭐ | $$$ | Pro-grade systems | | TLC | 3 | ⭐⭐ | ⭐⭐ | $$ | Consumer, gaming | | QLC | 4 | ⭐ | ⭐ | $ | Budget SSDs, media storage |
6. 3D NAND / V-NAND Technology
- Traditional NAND: Planar (flat) design.
- 3D NAND: Stacks cells vertically—more density, less space.
- Benefits:
- Greater capacity
- Better power efficiency
- Improved lifespan
Samsung’s V-NAND is a branded 3D NAND variant known for high endurance and stability.
7. Performance & Generational Comparison
| PCIe Gen | Max Speed | Use Case | |--------------|---------------|----------------------------------| | Gen 3 | ~3,500 MB/s | Mainstream laptops/desktops | | Gen 4 | ~7,000 MB/s | Gaming, prosumer, light servers | | Gen 5 | ~14,000 MB/s | AI workloads, enterprise |
Drives are backward compatible, but will operate at the host’s maximum supported speed.
8. Thermal Management
- NVMe SSDs generate heat—especially Gen 4/5.
- Heatsinks and thermal pads are vital for:
- Sustained performance (prevent throttling)
- Longer lifespan
- Recommended to leave 10–20% free space for optimal SSD wear leveling and garbage collection.
9. HDD vs SSD: Summary
| Aspect | HDD | SSD | |------------------|---------------------|------------------------------| | Speed | 80–160 MB/s | 550 MB/s – 14,000 MB/s | | Durability | Low (mechanical) | High (no moving parts) | | Lifespan | Moderate | High (depends on NAND type) | | Cost | Lower per GB | Higher per GB | | Noise | Audible | Silent |
10. Brand Recommendations
| Brand | Strength | |------------------|-----------------------------------------| | Samsung | Leading in performance (980 Pro, 990 Pro) | | Western Digital | Reliable Gen 3/4/5 drives (SN770, SN850X) | | Crucial | Budget-friendly, solid TLC drives (P3, P5 Plus) | | Kingston | Value-oriented SSDs (A2000, NV2) |
11. How to Choose the Right SSD
- Check your device slot: Is it M.2 B+M, M-key, or SATA-only?
- Interface compatibility: Confirm if the M.2 slot supports NVMe or only SATA.
- Match PCIe Gen: Use Gen 3/4/5 based on CPU/motherboard lanes.
- Pick NAND type: TLC for best balance of speed/longevity.
- Thermal plan: Use heatsinks or fans for Gen 4+ drives.
- Capacity need: Leave headroom (15–20%) for performance and lifespan.
- Trustworthy brands: Stick to Samsung, WD, Crucial for warranty and quality.
Consider
From boot speed to data integrity, SSDs have revolutionized how modern systems handle storage. While HDDs remain relevant for mass archival, NVMe SSDs—especially those leveraging PCIe Gen 4 and Gen 5—dominate in speed-critical workflows. M.2 NVMe is the dominant form factor for futureproof builds, while understanding memory types like TLC vs. QLC ensures better longevity planning.
Whether you’re upgrading a laptop, building a gaming rig, or running a self-hosted Bitcoin node, choosing the right form factor, interface, and NAND type can dramatically impact system performance and reliability.
Resources & Further Reading
- How-Fixit Storage Guides
- Kingston SSD Reliability Guide
- Western Digital Product Lines
- Samsung V-NAND Explained
- PCIe Gen 5 Benchmarks
Options
🔧 Recommended SSDs and Tools (Amazon)
-
Kingston A400 240GB SSD – SATA 3 2.5"
https://a.co/d/41esjYL -
Samsung 970 EVO Plus 2TB NVMe M.2 SSD – Gen 3
https://a.co/d/6EMVAN1 -
Crucial P5 Plus 1TB PCIe Gen4 NVMe M.2 SSD
https://a.co/d/hQx50Cq -
WD Blue SN570 1TB NVMe SSD – PCIe Gen 3
https://a.co/d/j2zSDCJ -
Sabrent Rocket Q 2TB NVMe SSD – QLC NAND
https://a.co/d/325Og2K -
Thermalright M.2 SSD Heatsink Kit
https://a.co/d/0IYH3nK -
ORICO M.2 NVMe SSD Enclosure – USB 3.2 Gen2
https://a.co/d/aEwQmih
🛠️ DIY & Fix Resource
- How-Fixit – PC Repair Guides and Tutorials
https://www.how-fixit.com/
In Addition
Modern Storage Technologies and Mini NAS Implementation
1. Network Attached Storage (NAS) system
In the rapidly evolving landscape of data storage, understanding the nuances of various storage technologies is crucial for optimal system design and performance. This idea delves into the distinctions between traditional Hard Disk Drives (HDDs), Solid State Drives (SSDs), and advanced storage interfaces like M.2 NVMe, M.2 SATA, and mSATA. Additionally, it explores the implementation of a compact Network Attached Storage (NAS) system using the Nookbox G9, highlighting its capabilities and limitations.
2. Storage Technologies Overview
2.1 Hard Disk Drives (HDDs)
- Mechanism: Utilize spinning magnetic platters and read/write heads.
- Advantages:
- Cost-effective for large storage capacities.
- Longer lifespan in low-vibration environments.
- Disadvantages:
- Slower data access speeds.
- Susceptible to mechanical failures due to moving parts.
2.2 Solid State Drives (SSDs)
- Mechanism: Employ NAND flash memory with no moving parts.
- Advantages:
- Faster data access and boot times.
- Lower power consumption and heat generation.
- Enhanced durability and shock resistance.
- Disadvantages:
- Higher cost per gigabyte compared to HDDs.
- Limited write cycles, depending on NAND type.
3. SSD Form Factors and Interfaces
3.1 Form Factors
- 2.5-Inch: Standard size for laptops and desktops; connects via SATA interface.
- mSATA: Miniature SATA interface, primarily used in ultrabooks and embedded systems; largely supplanted by M.2.
- M.2: Versatile form factor supporting both SATA and NVMe interfaces; prevalent in modern systems.
3.2 Interfaces
- SATA (Serial ATA):
- Speed: Up to 600 MB/s.
- Compatibility: Widely supported across various devices.
-
Limitation: Bottleneck for high-speed SSDs.
-
NVMe (Non-Volatile Memory Express):
- Speed: Ranges from 3,500 MB/s (PCIe Gen 3) to over 14,000 MB/s (PCIe Gen 5).
- Advantage: Direct communication with CPU via PCIe lanes, reducing latency.
- Consideration: Requires compatible motherboard and BIOS support.
4. M.2 SATA vs. M.2 NVMe
| Feature | M.2 SATA | M.2 NVMe | |------------------------|--------------------------------------------------|----------------------------------------------------| | Interface | SATA III (AHCI protocol) | PCIe (NVMe protocol) | | Speed | Up to 600 MB/s | Up to 14,000 MB/s (PCIe Gen 5) | | Compatibility | Broad compatibility with older systems | Requires NVMe-compatible M.2 slot and BIOS support | | Use Case | Budget builds, general computing | High-performance tasks, gaming, content creation |
Note: M.2 NVMe drives are not backward compatible with M.2 SATA slots due to differing interfaces and keying.
5. NAND Flash Memory Types
Understanding NAND types is vital for assessing SSD performance and longevity.
- SLC (Single-Level Cell):
- Bits per Cell: 1
- Endurance: ~100,000 write cycles
-
Use Case: Enterprise and industrial applications
-
MLC (Multi-Level Cell):
- Bits per Cell: 2
- Endurance: ~10,000 write cycles
-
Use Case: Consumer-grade SSDs
-
TLC (Triple-Level Cell):
- Bits per Cell: 3
- Endurance: ~3,000 write cycles
-
Use Case: Mainstream consumer SSDs
-
QLC (Quad-Level Cell):
- Bits per Cell: 4
- Endurance: ~1,000 write cycles
-
Use Case: Read-intensive applications
-
3D NAND:
- Structure: Stacks memory cells vertically to increase density.
- Advantage: Enhances performance and endurance across NAND types.
6. Thermal Management and SSD Longevity
Effective thermal management is crucial for maintaining SSD performance and lifespan.
- Heatsinks: Aid in dissipating heat from SSD controllers.
- Airflow: Ensuring adequate case ventilation prevents thermal throttling.
- Monitoring: Regularly check SSD temperatures, especially under heavy workloads.
7. Trusted SSD Manufacturers
Selecting SSDs from reputable manufacturers ensures reliability and support.
- Samsung: Known for high-performance SSDs with robust software support.
- Western Digital (WD): Offers a range of SSDs catering to various user needs.
- Crucial (Micron): Provides cost-effective SSD solutions with solid performance.
8. Mini NAS Implementation: Nookbox G9 Case Study
8.1 Overview
The Nookbox G9 is a compact NAS solution designed to fit within a 1U rack space, accommodating four M.2 NVMe SSDs.
8.2 Specifications
- Storage Capacity: Supports up to 8TB using four 2TB NVMe SSDs.
- Interface: Each M.2 slot operates at PCIe Gen 3x2.
- Networking: Equipped with 2.5 Gigabit Ethernet ports.
- Operating System: Comes pre-installed with Windows 11; compatible with Linux distributions like Ubuntu 24.10.
8.3 Performance and Limitations
- Throughput: Network speeds capped at ~250 MB/s due to 2.5 GbE limitation.
- Thermal Issues: Inadequate cooling leads to SSD temperatures reaching up to 80°C under load, causing potential throttling and system instability.
- Reliability: Reports of system reboots and lockups during intensive operations, particularly with ZFS RAIDZ configurations.
8.4 Recommendations
- Cooling Enhancements: Implement third-party heatsinks to improve thermal performance.
- Alternative Solutions: Consider NAS systems with better thermal designs and higher network throughput for demanding applications.
9. Consider
Navigating the myriad of storage technologies requires a comprehensive understanding of form factors, interfaces, and memory types. While HDDs offer cost-effective bulk storage, SSDs provide superior speed and durability. The choice between M.2 SATA and NVMe hinges on performance needs and system compatibility. Implementing compact NAS solutions like the Nookbox G9 necessitates careful consideration of thermal management and network capabilities to ensure reliability and performance.
Product Links (Amazon)
-
Thermal Heatsink for M.2 SSDs (Must-have for stress and cooling)
https://a.co/d/43B1F3t -
Nookbox G9 – Mini NAS
https://a.co/d/3dswvGZ -
Alternative 1: Possibly related cooling or SSD gear
https://a.co/d/c0Eodm3 -
Alternative 2: Possibly related NAS accessories or SSDs
https://a.co/d/9gWeqDr
Benchmark Results (Geekbench)
-
GMKtec G9 Geekbench CPU Score #1
https://browser.geekbench.com/v6/cpu/11471182 -
GMKtec G9 Geekbench CPU Score #2
https://browser.geekbench.com/v6/cpu/11470130 -
GMKtec Geekbench User Profile
https://browser.geekbench.com/user/446940
-
 @ 04ea4f83:210e1713
2025-05-01 17:59:51
@ 04ea4f83:210e1713
2025-05-01 17:59:51In nicht allzu vielen Jahren wird die Zahl der Bitcoiner in den Vereinigten Staaten von Amerika zehn Millionen überschreiten. Wenn wir diesen Meilenstein erreichen, ist das Spiel vorbei: Bitcoin gewinnt.
Mein Lieblingsautor und -denker, Nassim Nicholas Taleb, schrieb in seinem Buch Skin in the Game über "die unnachgiebige Minderheit". Das Konzept funktioniert folgendermaßen: Auf fast allen verpackten Lebensmitteln, die in den USA verkauft werden, ist außen ein kleines U in einem Kreis aufgedruckt. Nur sehr wenige US-Bürger benötigen die durch dieses U gekennzeichnete Koscher-Zertifizierung, aber für die Lebensmittelhersteller ist es einfacher, nicht für jedes Produkt zwei separate Versionen zu produzieren, so dass sie im Allgemeinen alles koscher machen. Nach Taleb gilt die Regel: „Ein koscherer Esser wird niemals nicht-koschere Lebensmittel essen, aber einem nicht-koscheren Esser ist es nicht verboten, koscher zu essen."
„Bei den meisten beobachteten komplexen Systemen liegt der Anteil der Minderheit, der erforderlich ist, um die Bevölkerung von ihrer unnachgiebigen Meinung abzubringen, in der Größenordnung von 3 bis 4%. Bei einer US-Bevölkerung von 325 Millionen sind 3% 10 Millionen." - Nassim Nicholas Taleb
Ein Fintech-Fonds, der seit 2012 im Bitcoin-Bereich tätig ist, hat kürzlich eine intensive Analyse durchgeführt, die zur besten Schätzung des Bitcoin-Besitzes geführt hat, die ich kenne. Nur 7 Millionen Menschen weltweit haben einen Wert von 100 Dollar oder mehr im Bitcoin-Protokoll gespeichert. Um die Zahlen zu runden, nehmen wir an, dass die Hälfte dieser Menschen in den USA lebt und dass ein Siebtel von ihnen einen höheren Wert als $2500 in BTC speichert. Das sind gerade einmal 500.000 US-Bürger mit einer bedeutenden Menge an Bitcoin. Und wie viel Prozent davon verstehen und interessieren sich tatsächlich so sehr für Bitcoin, dass sie dafür kämpfen würden? Lass uns großzügig sein und sagen wir 20%.
Es gibt ungefähr 100.000 Bitcoiner in den Vereinigten Staaten. Das bedeutet, dass wir eine 100-fache Steigerung benötigen, um das Niveau einer "unnachgiebigen Minderheit" zu erreichen. Das ist der Grund, warum die Akzeptanz alle anderen Prioritäten für Bitcoin dominiert.
„Bitcoiner haben bereits so viele potentielle Angriffsvektoren ausgeschaltet und so viel FUD gehandhabt, dass es nicht mehr viel Abwärtsrisiko für Bitcoin gibt." - Cory Klippsten
Ein weiteres Konzept, auf das sich Taleb in den fünf Bänden seines Incerto bezieht, ist: Schütze dich vor dem Abwärtsrisiko. Bitcoiner haben bereits so viele potentielle Angriffsvektoren ausgeschaltet und so viel FUD gehandhabt, dass es nicht mehr viel Abwärtsrisiko für Bitcoin gibt. Aber es gibt ein gewisses Risiko, egal ob man es mit unter 1%, unter 10% oder mehr beziffert. Und der bei weitem bedrohlichste Angriffsvektor wäre meiner Meinung nach eine konzertierte Aktion der US-Regierung auf vielen Ebenen, die versucht, Bitcoin auszurotten, um die Hegemonie des Dollars auf der ganzen Welt zu erhalten.
Um es klar zu sagen: Bitcoin würde selbst den konzertiertesten und bösartigsten Angriff der US-Regierung überleben. Er könnte sogar gedeihen, im Stil von Antifragile (ein weiteres Buch von Taleb), mit Menschen auf der ganzen Welt, die massenhaft Sats kaufen, wenn sie sehen, wie der frühere Hegemon ausschlägt. Es könnte aber auch anders kommen, mit einem massiven Rückgang der Netzwerkaktivität und des gespeicherten Wertes, mit Tausenden von Menschenleben, die irreparabel gestört werden, und mit einer Verzögerung unserer leuchtend orangenen Zukunft um Jahrzehnte oder länger.
Das ist für mich nicht hinnehmbar. Deshalb habe ich mein Leben der Rekrutierung der anderen 99% unserer unnachgiebigen Bitcoiner-Minderheit hier in den Vereinigten Staaten gewidmet. Es gibt bereits 100.000 von uns. Helfe mit, die anderen 9,9 Millionen zu rekrutieren.
-
 @ 3bf0c63f:aefa459d
2025-04-25 19:26:48
@ 3bf0c63f:aefa459d
2025-04-25 19:26:48Redistributing Git with Nostr
Every time someone tries to "decentralize" Git -- like many projects tried in the past to do it with BitTorrent, IPFS, ScuttleButt or custom p2p protocols -- there is always a lurking comment: "but Git is already distributed!", and then the discussion proceeds to mention some facts about how Git supports multiple remotes and its magic syncing and merging abilities and so on.
Turns out all that is true, Git is indeed all that powerful, and yet GitHub is the big central hub that hosts basically all Git repositories in the giant world of open-source. There are some crazy people that host their stuff elsewhere, but these projects end up not being found by many people, and even when they do they suffer from lack of contributions.
Because everybody has a GitHub account it's easy to open a pull request to a repository of a project you're using if it's on GitHub (to be fair I think it's very annoying to have to clone the repository, then add it as a remote locally, push to it, then go on the web UI and click to open a pull request, then that cloned repository lurks forever in your profile unless you go through 16 screens to delete it -- but people in general seem to think it's easy).
It's much harder to do it on some random other server where some project might be hosted, because now you have to add 4 more even more annoying steps: create an account; pick a password; confirm an email address; setup SSH keys for pushing. (And I'm not even mentioning the basic impossibility of offering
pushaccess to external unknown contributors to people who want to host their own simple homemade Git server.)At this point some may argue that we could all have accounts on GitLab, or Codeberg or wherever else, then those steps are removed. Besides not being a practical strategy this pseudo solution misses the point of being decentralized (or distributed, who knows) entirely: it's far from the ideal to force everybody to have the double of account management and SSH setup work in order to have the open-source world controlled by two shady companies instead of one.
What we want is to give every person the opportunity to host their own Git server without being ostracized. at the same time we must recognize that most people won't want to host their own servers (not even most open-source programmers!) and give everybody the ability to host their stuff on multi-tenant servers (such as GitHub) too. Importantly, though, if we allow for a random person to have a standalone Git server on a standalone server they host themselves on their wood cabin that also means any new hosting company can show up and start offering Git hosting, with or without new cool features, charging high or low or zero, and be immediately competing against GitHub or GitLab, i.e. we must remove the network-effect centralization pressure.
External contributions
The first problem we have to solve is: how can Bob contribute to Alice's repository without having an account on Alice's server?
SourceHut has reminded GitHub users that Git has always had this (for most) arcane
git send-emailcommand that is the original way to send patches, using an once-open protocol.Turns out Nostr acts as a quite powerful email replacement and can be used to send text content just like email, therefore patches are a very good fit for Nostr event contents.
Once you get used to it and the proper UIs (or CLIs) are built sending and applying patches to and from others becomes a much easier flow than the intense clickops mixed with terminal copypasting that is interacting with GitHub (you have to clone the repository on GitHub, then update the remote URL in your local directory, then create a branch and then go back and turn that branch into a Pull Request, it's quite tiresome) that many people already dislike so much they went out of their way to build many GitHub CLI tools just so they could comment on issues and approve pull requests from their terminal.
Replacing GitHub features
Aside from being the "hub" that people use to send patches to other people's code (because no one can do the email flow anymore, justifiably), GitHub also has 3 other big features that are not directly related to Git, but that make its network-effect harder to overcome. Luckily Nostr can be used to create a new environment in which these same features are implemented in a more decentralized and healthy way.
Issues: bug reports, feature requests and general discussions
Since the "Issues" GitHub feature is just a bunch of text comments it should be very obvious that Nostr is a perfect fit for it.
I will not even mention the fact that Nostr is much better at threading comments than GitHub (which doesn't do it at all), which can generate much more productive and organized discussions (and you can opt out if you want).
Search
I use GitHub search all the time to find libraries and projects that may do something that I need, and it returns good results almost always. So if people migrated out to other code hosting providers wouldn't we lose it?
The fact is that even though we think everybody is on GitHub that is a globalist falsehood. Some projects are not on GitHub, and if we use only GitHub for search those will be missed. So even if we didn't have a Nostr Git alternative it would still be necessary to create a search engine that incorporated GitLab, Codeberg, SourceHut and whatnot.
Turns out on Nostr we can make that quite easy by not forcing anyone to integrate custom APIs or hardcoding Git provider URLs: each repository can make itself available by publishing an "announcement" event with a brief description and one or more Git URLs. That makes it easy for a search engine to index them -- and even automatically download the code and index the code (or index just README files or whatever) without a centralized platform ever having to be involved.
The relays where such announcements will be available play a role, of course, but that isn't a bad role: each announcement can be in multiple relays known for storing "public good" projects, some relays may curate only projects known to be very good according to some standards, other relays may allow any kind of garbage, which wouldn't make them good for a search engine to rely upon, but would still be useful in case one knows the exact thing (and from whom) they're searching for (the same is valid for all Nostr content, by the way, and that's where it's censorship-resistance comes from).
Continuous integration
GitHub Actions are a very hardly subsidized free-compute-for-all-paid-by-Microsoft feature, but one that isn't hard to replace at all. In fact there exists today many companies offering the same kind of service out there -- although they are mostly targeting businesses and not open-source projects, before GitHub Actions was introduced there were also many that were heavily used by open-source projects.
One problem is that these services are still heavily tied to GitHub today, they require a GitHub login, sometimes BitBucket and GitLab and whatnot, and do not allow one to paste an arbitrary Git server URL, but that isn't a thing that is very hard to change anyway, or to start from scratch. All we need are services that offer the CI/CD flows, perhaps using the same framework of GitHub Actions (although I would prefer to not use that messy garbage), and charge some few satoshis for it.
It may be the case that all the current services only support the big Git hosting platforms because they rely on their proprietary APIs, most notably the webhooks dispatched when a repository is updated, to trigger the jobs. It doesn't have to be said that Nostr can also solve that problem very easily.
-
 @ c1e9ab3a:9cb56b43
2025-05-01 17:29:18
@ c1e9ab3a:9cb56b43
2025-05-01 17:29:18High-Level Overview
Bitcoin developers are currently debating a proposed change to how Bitcoin Core handles the
OP_RETURNopcode — a mechanism that allows users to insert small amounts of data into the blockchain. Specifically, the controversy revolves around removing built-in filters that limit how much data can be stored using this feature (currently capped at 80 bytes).Summary of Both Sides
Position A: Remove OP_RETURN Filters
Advocates: nostr:npub1ej493cmun8y9h3082spg5uvt63jgtewneve526g7e2urca2afrxqm3ndrm, nostr:npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vg, nostr:npub17u5dneh8qjp43ecfxr6u5e9sjamsmxyuekrg2nlxrrk6nj9rsyrqywt4tp, others
Arguments: - Ineffectiveness of filters: Filters are easily bypassed and do not stop spam effectively. - Code simplification: Removing arbitrary limits reduces code complexity. - Permissionless innovation: Enables new use cases like cross-chain bridges and timestamping without protocol-level barriers. - Economic regulation: Fees should determine what data gets added to the blockchain, not protocol rules.
Position B: Keep OP_RETURN Filters
Advocates: nostr:npub1lh273a4wpkup00stw8dzqjvvrqrfdrv2v3v4t8pynuezlfe5vjnsnaa9nk, nostr:npub1s33sw6y2p8kpz2t8avz5feu2n6yvfr6swykrnm2frletd7spnt5qew252p, nostr:npub1wnlu28xrq9gv77dkevck6ws4euej4v568rlvn66gf2c428tdrptqq3n3wr, others
Arguments: - Historical intent: Satoshi included filters to keep Bitcoin focused on monetary transactions. - Resource protection: Helps prevent blockchain bloat and abuse from non-financial uses. - Network preservation: Protects the network from being overwhelmed by low-value or malicious data. - Social governance: Maintains conservative changes to ensure long-term robustness.
Strengths and Weaknesses
Strengths of Removing Filters
- Encourages decentralized innovation.
- Simplifies development and maintenance.
- Maintains ideological purity of a permissionless system.
Weaknesses of Removing Filters
- Opens the door to increased non-financial data and potential spam.
- May dilute Bitcoin’s core purpose as sound money.
- Risks short-term exploitation before economic filters adapt.
Strengths of Keeping Filters
- Preserves Bitcoin’s identity and original purpose.
- Provides a simple protective mechanism against abuse.
- Aligns with conservative development philosophy of Bitcoin Core.
Weaknesses of Keeping Filters
- Encourages central decision-making on allowed use cases.
- Leads to workarounds that may be less efficient or obscure.
- Discourages novel but legitimate applications.
Long-Term Consequences
If Filters Are Removed
- Positive: Potential boom in new applications, better interoperability, cleaner architecture.
- Negative: Risk of increased blockchain size, more bandwidth/storage costs, spam wars.
If Filters Are Retained
- Positive: Preserves monetary focus and operational discipline.
- Negative: Alienates developers seeking broader use cases, may ossify the protocol.
Conclusion
The debate highlights a core philosophical split in Bitcoin: whether it should remain a narrow monetary system or evolve into a broader data layer for decentralized applications. Both paths carry risks and tradeoffs. The outcome will shape not just Bitcoin's technical direction but its social contract and future role in the broader crypto ecosystem.
-
 @ 3bf0c63f:aefa459d
2025-04-25 18:55:52
@ 3bf0c63f:aefa459d
2025-04-25 18:55:52Report of how the money Jack donated to the cause in December 2022 has been misused so far.
Bounties given
March 2025
- Dhalsim: 1,110,540 - Work on Nostr wiki data processing
February 2025
- BOUNTY* NullKotlinDev: 950,480 - Twine RSS reader Nostr integration
- Dhalsim: 2,094,584 - Work on Hypothes.is Nostr fork
- Constant, Biz and J: 11,700,588 - Nostr Special Forces
January 2025
- Constant, Biz and J: 11,610,987 - Nostr Special Forces
- BOUNTY* NullKotlinDev: 843,840 - Feeder RSS reader Nostr integration
- BOUNTY* NullKotlinDev: 797,500 - ReadYou RSS reader Nostr integration
December 2024
- BOUNTY* tijl: 1,679,500 - Nostr integration into RSS readers yarr and miniflux
- Constant, Biz and J: 10,736,166 - Nostr Special Forces
- Thereza: 1,020,000 - Podcast outreach initiative
November 2024
- Constant, Biz and J: 5,422,464 - Nostr Special Forces
October 2024
- Nostrdam: 300,000 - hackathon prize
- Svetski: 5,000,000 - Latin America Nostr events contribution
- Quentin: 5,000,000 - nostrcheck.me
June 2024
- Darashi: 5,000,000 - maintaining nos.today, searchnos, search.nos.today and other experiments
- Toshiya: 5,000,000 - keeping the NIPs repo clean and other stuff
May 2024
- James: 3,500,000 - https://github.com/jamesmagoo/nostr-writer
- Yakihonne: 5,000,000 - spreading the word in Asia
- Dashu: 9,000,000 - https://github.com/haorendashu/nostrmo
February 2024
- Viktor: 5,000,000 - https://github.com/viktorvsk/saltivka and https://github.com/viktorvsk/knowstr
- Eric T: 5,000,000 - https://github.com/tcheeric/nostr-java
- Semisol: 5,000,000 - https://relay.noswhere.com/ and https://hist.nostr.land relays
- Sebastian: 5,000,000 - Drupal stuff and nostr-php work
- tijl: 5,000,000 - Cloudron, Yunohost and Fraidycat attempts
- Null Kotlin Dev: 5,000,000 - AntennaPod attempt
December 2023
- hzrd: 5,000,000 - Nostrudel
- awayuki: 5,000,000 - NOSTOPUS illustrations
- bera: 5,000,000 - getwired.app
- Chris: 5,000,000 - resolvr.io
- NoGood: 10,000,000 - nostrexplained.com stories
October 2023
- SnowCait: 5,000,000 - https://nostter.vercel.app/ and other tools
- Shaun: 10,000,000 - https://yakihonne.com/, events and work on Nostr awareness
- Derek Ross: 10,000,000 - spreading the word around the world
- fmar: 5,000,000 - https://github.com/frnandu/yana
- The Nostr Report: 2,500,000 - curating stuff
- james magoo: 2,500,000 - the Obsidian plugin: https://github.com/jamesmagoo/nostr-writer
August 2023
- Paul Miller: 5,000,000 - JS libraries and cryptography-related work
- BOUNTY tijl: 5,000,000 - https://github.com/github-tijlxyz/wikinostr
- gzuus: 5,000,000 - https://nostree.me/
July 2023
- syusui-s: 5,000,000 - rabbit, a tweetdeck-like Nostr client: https://syusui-s.github.io/rabbit/
- kojira: 5,000,000 - Nostr fanzine, Nostr discussion groups in Japan, hardware experiments
- darashi: 5,000,000 - https://github.com/darashi/nos.today, https://github.com/darashi/searchnos, https://github.com/darashi/murasaki
- jeff g: 5,000,000 - https://nostr.how and https://listr.lol, plus other contributions
- cloud fodder: 5,000,000 - https://nostr1.com (open-source)
- utxo.one: 5,000,000 - https://relaying.io (open-source)
- Max DeMarco: 10,269,507 - https://www.youtube.com/watch?v=aA-jiiepOrE
- BOUNTY optout21: 1,000,000 - https://github.com/optout21/nip41-proto0 (proposed nip41 CLI)
- BOUNTY Leo: 1,000,000 - https://github.com/leo-lox/camelus (an old relay thing I forgot exactly)
June 2023
- BOUNTY: Sepher: 2,000,000 - a webapp for making lists of anything: https://pinstr.app/
- BOUNTY: Kieran: 10,000,000 - implement gossip algorithm on Snort, implement all the other nice things: manual relay selection, following hints etc.
- Mattn: 5,000,000 - a myriad of projects and contributions to Nostr projects: https://github.com/search?q=owner%3Amattn+nostr&type=code
- BOUNTY: lynn: 2,000,000 - a simple and clean git nostr CLI written in Go, compatible with William's original git-nostr-tools; and implement threaded comments on https://github.com/fiatjaf/nocomment.
- Jack Chakany: 5,000,000 - https://github.com/jacany/nblog
- BOUNTY: Dan: 2,000,000 - https://metadata.nostr.com/
April 2023
- BOUNTY: Blake Jakopovic: 590,000 - event deleter tool, NIP dependency organization
- BOUNTY: koalasat: 1,000,000 - display relays
- BOUNTY: Mike Dilger: 4,000,000 - display relays, follow event hints (Gossip)
- BOUNTY: kaiwolfram: 5,000,000 - display relays, follow event hints, choose relays to publish (Nozzle)
- Daniele Tonon: 3,000,000 - Gossip
- bu5hm4nn: 3,000,000 - Gossip
- BOUNTY: hodlbod: 4,000,000 - display relays, follow event hints
March 2023
- Doug Hoyte: 5,000,000 sats - https://github.com/hoytech/strfry
- Alex Gleason: 5,000,000 sats - https://gitlab.com/soapbox-pub/mostr
- verbiricha: 5,000,000 sats - https://badges.page/, https://habla.news/
- talvasconcelos: 5,000,000 sats - https://migrate.nostr.com, https://read.nostr.com, https://write.nostr.com/
- BOUNTY: Gossip model: 5,000,000 - https://camelus.app/
- BOUNTY: Gossip model: 5,000,000 - https://github.com/kaiwolfram/Nozzle
- BOUNTY: Bounty Manager: 5,000,000 - https://nostrbounties.com/
February 2023
- styppo: 5,000,000 sats - https://hamstr.to/
- sandwich: 5,000,000 sats - https://nostr.watch/
- BOUNTY: Relay-centric client designs: 5,000,000 sats https://bountsr.org/design/2023/01/26/relay-based-design.html
- BOUNTY: Gossip model on https://coracle.social/: 5,000,000 sats
- Nostrovia Podcast: 3,000,000 sats - https://nostrovia.org/
- BOUNTY: Nostr-Desk / Monstr: 5,000,000 sats - https://github.com/alemmens/monstr
- Mike Dilger: 5,000,000 sats - https://github.com/mikedilger/gossip
January 2023
- ismyhc: 5,000,000 sats - https://github.com/Galaxoid-Labs/Seer
- Martti Malmi: 5,000,000 sats - https://iris.to/
- Carlos Autonomous: 5,000,000 sats - https://github.com/BrightonBTC/bija
- Koala Sat: 5,000,000 - https://github.com/KoalaSat/nostros
- Vitor Pamplona: 5,000,000 - https://github.com/vitorpamplona/amethyst
- Cameri: 5,000,000 - https://github.com/Cameri/nostream
December 2022
- William Casarin: 7 BTC - splitting the fund
- pseudozach: 5,000,000 sats - https://nostr.directory/
- Sondre Bjellas: 5,000,000 sats - https://notes.blockcore.net/
- Null Dev: 5,000,000 sats - https://github.com/KotlinGeekDev/Nosky
- Blake Jakopovic: 5,000,000 sats - https://github.com/blakejakopovic/nostcat, https://github.com/blakejakopovic/nostreq and https://github.com/blakejakopovic/NostrEventPlayground
-
 @ 4d41a7cb:7d3633cc
2025-05-01 17:13:17
@ 4d41a7cb:7d3633cc
2025-05-01 17:13:17Did you know that Federal Reserve Notes (FRNs), commonly known as "us dollars" are broken contracts? In fact FRNs started as dollar IOUs and then the Federal Reserve (a private corporation) defaulted on its debts and made the U.S citizens pay the bill: effectively stealing the privately owned gold.
The United States Dollar
It is not that the dollar was "backed by gold" as it is commonly said. The dollar was primally a measure of weight of silver and then a measure of weight of gold. Let see a little history about the U.S dollar.
What does the constitution says?
Article I, Section 8:
This section grants Congress the power "to coin money, regulate the value thereof, and of foreign coin, and fix the standard of weights and measures."
Article I, Section 10:
"No State shall... make any Thing but gold and silver Coin a Tender in Payment of Debts."
The United States government, by decree, created the dollar as measure of weight defined by the Coinage Act of 1792 as 371.25 grains (24 grams) of silver.
The 1794 silver dollar, known as the "Flowing Hair dollar," was the first silver dollar coin produced by the United States Mint. This was the original dollar! The were minted in $1, $0,5.
 In 1795 the United States minted its first gold coins under the Coinage Act of 1792, which introduced the following denominations: $2,5, $5 and $10. The silver to gold ratio was fixed at 1:15, meaning 15 ounces of silver was the equivalent to one ounce of gold.
In 1795 the United States minted its first gold coins under the Coinage Act of 1792, which introduced the following denominations: $2,5, $5 and $10. The silver to gold ratio was fixed at 1:15, meaning 15 ounces of silver was the equivalent to one ounce of gold.Individuals could bring silver bullion to the U.S. Mint and have it coined into legal tender.
 ## Coinage acts
## Coinage actsThe Coinage Act of 1834 adjusted the gold-to-silver ratio to 16:1 and and the weight of the gold coins because gold was undervalue and encouraging the melting and exporting of American gold.
The coinage act of 1837 defined the silver dollar as containing 412.5 grains of standard silver (90% silver and 10% copper) and it reinforced the legal tender status of these coins, ensuring their acceptance for all debts, public and private.
The Coinage Act of 1849 specifically addressed the introduction of new gold denominations in response to the California Gold Rush, which significantly increased gold supplies in the United States. The Act authorized the minting of a $1 gold coin, the smallest gold denomination ever issued by the United States. The Act also authorized the creation of the $20 gold coin, known as the Double Eagle.
The gold dollar coin contained 23.22 grains of pure gold or 1.505grams or 0.0484 troy ounces.
 The Double Eagle contained 464.4 grains of pure gold or 30.093 grams, 0.968 troy ounces.
The Double Eagle contained 464.4 grains of pure gold or 30.093 grams, 0.968 troy ounces. The coinage act of 1857 sought to establish a uniform domestic currency and reduce reliance on foreign coins, demonetizing every foreign coins as legal tender. This was also the beginning of the Flying Eagle cent, which was smaller in diameter and composed of 88% copper and 12% nickel. This centralized more the coinage in the U.S.
The coinage act of 1857 sought to establish a uniform domestic currency and reduce reliance on foreign coins, demonetizing every foreign coins as legal tender. This was also the beginning of the Flying Eagle cent, which was smaller in diameter and composed of 88% copper and 12% nickel. This centralized more the coinage in the U.S.U.S Gold certificates
The Act of March 3, 1863, officially known as the National Bank Act, was a significant piece of legislation during the American Civil War aimed at creating a national banking system and establishing a uniform national currency.
This legislation allowed the U.S. Treasury to issue gold certificates, which served as a form of paper currency backed by gold. The introduction of gold certificates was primarily intended to facilitate transactions involving gold without the need for the physical transfer of the metal.
This was primary for large size comercial transactions or payments among banks.
1865 Series
 "It is hereby certified that one hundred dollars have been deposited with the assistant treasurer of the U.S in New York payable in GOLD at his office in the xxx New York "
"It is hereby certified that one hundred dollars have been deposited with the assistant treasurer of the U.S in New York payable in GOLD at his office in the xxx New York "The coinage act of 1873 also known as the "crime of 1873" was the intent to demonetize silver by ceasing the minting of silver dollars which meant that citizens could no longer bring silver to the mint to be coined into legal tender. By stopping the production of silver dollars, the Act implicitly placed the U.S. on a gold standard, where gold, not silver, was the primary basis for currency. This had lasting economic effects, particularly on farmers and silver miners who preferred bimetallism (the use of both gold and silver as standards).
The Act was controversial, particularly in western and rural areas where silver was a significant economic factor. Many believed that the Act was passed to benefit creditors and large financial interests by adopting a gold standard, which tended to deflate prices and increase the value of money.
The coinage act of 1878, The Act mandated the U.S. Treasury to purchase a specified amount of silver each month, between two million and four million dollars worth, and to mint it into silver dollars. This marked a partial return to the use of silver as currency through the coinage of the standard silver dollar. The Act allowed for the issuance of silver certificates, which could be used as currency in place of actual silver coins, thus easing the circulation of silver-backed currency.
The Bland-Allison Act was passed against a backdrop of economic depression and agrarian unrest. It represented a compromise between advocates of the gold standard and those wishing to return to bimetallism.
1882 series
 The 30 years of economic and political discourse between bimetallism supporters and gold only advocates finally ended in the 1900.
The 30 years of economic and political discourse between bimetallism supporters and gold only advocates finally ended in the 1900.The Gold Standard Act of 1900
The Gold Standard Act of 1900 formalized the monetary system of the United States by establishing gold as the sole standard for redeeming paper money and effectively ending the bimetallic standard. It established that the gold dollar would be the standard unit of value, equating the dollar to 25.8 grains of gold at a purity of 90%. Silver certificates and silver coins remained in circulation but without the backing of free and unlimited coinage.
Let's remember that the dollar was still a measure of gold. The certificates where government IOUs for that gold that was deposited in the treasury of the United States.
1907 series of gold certificates:

## The Federal Reserve Act of 1913
The Federal Reserva Act of 1913 created a monopoly over the issuance of the American paper currency. This marked the privatization of the currency and a centralization of power like never before. More about this in another article.
But essentially the secret agenda of banksters was to issue IOUs without any restriction and make the United State Government responsible to redeem this paper currency for gold. And I will show you exactly how. Alfred Owen Crozier wrote a book in 1912 one year before the bill was passed analyzing and opposing it and made this same argument.
Federal Reserve Notes
A paper contract, a promissory note, an "I owe you x amount"
This paper currency issued by this private central bank were dollar IOUs contracts or promissory notes.
According to Black's law dictionary a Federal Reserve note is: The paper currency in circulation in the United States. The notes are issued by the Federal Reserve Banks, are effectively non-interest-bearing promissory notes payable to bearer on demand, and are issued in denominations of $1, $5, $10, $20, $50, $100, $500, $1000, $5,000 and $10,000.
NON INTERES BEARING PROMISSORY NOTES.
A promissory note is a written, unconditional promise made by one party (the maker) to pay a definite sum of money to another party (the payee) or bearer, either on demand or at a specified future date. It is essentially a financial instrument representing a formal commitment to settle a specified monetary obligation.
Key Characteristics of a Promissory Note:
- Written Instrument: The promise to pay must be documented in writing.
- Unconditional Promise: The promise to pay cannot be contingent on any external factors or conditions.
- Definite Sum: The amount to be paid must be clearly specified and agreed upon in the note.
- Payee: The note must designate the person or entity to whom the payment is to be made either explicitly or implicitly by specifying it as payable "to bearer".
- Payable on Demand or at a Specific Time: The promissory note should indicate whether the payment is due upon demand by the payee or at a specific future date as agreed by the involved parties.
Promissory notes are commonly used in various financial transactions, including loans, business financing, and real estate deals, as they formalize the commitment to pay and can be enforced as a legal contract if necessary.
The Federal Reserve (FED) issued paper contract promising to be redeemable in gold. Most people never saw or understood the contract. Most never read it because the Fed cleverly hid the contract on the front of the bill by dividing it into five separate lines of text with a very different typeface for each line and placing the president's picture right in the middle. They even used the old lawyer's trick of hiding the most important text in small print.
Over time, the terms and conditions of the contract were watered down until they eventually became literally a promissory note for nothing. But let's analice how they did this step by step...
FEDERAL RESERVE NOTES: 1914 SERIES
 Content of the contract:
Content of the contract:Federal reserve note
The United States of America will pay to the bearer on demand: FIFTY DOLLARS
Authorized by federal reserve act of December 23, 1913
This note is receivable by all national and member banks and federal reserve banks and for all taxes, customs and other public dues. It is redeemable in gold on demand at the treasury department of the United States in the city of Washington district of Columbia or in gold or lawful money at any federal reserve bank.
So if a dollar was 20.67 per ounce, $50 could be exchanged for about 2.42 ounces of gold.
FEDERAL RESERVE NOTES :1918 SERIES
Content of the contract:
Federal reserve note
The United States of America will pay to the bearer on demand: Ten thousand dollars
Authorized by federal reserve act of December 23, 1913, as amended by act of September 26, 1918
This note is receivable by all national and member banks and federal reserve banks and for all taxes, customs and other public dues. It is redeemable in gold on demand at the treasury department of the United States in the city of Washington district of Columbia or in gold or lawful money at any federal reserve bank.
So if a dollar was 20.67 per ounce, $10,000 could be exchanged for 484.29ounces of gold.
Series of 1928
The great imitation
In 1928 the U.S government issued a new series of gold certificates payable to the bearer on demand.
 The same year the Federal Reserve issued it's own promissory notes copying the us government gold certificate's design:
The same year the Federal Reserve issued it's own promissory notes copying the us government gold certificate's design:Content of the contract:
Federal reserve note
The United States of America
will pay to the bearer on demand: One hundred dollars
Reedemable in gold on demand at the United States treasury, or in gold or lawful money, at any federal reserve bank.
So if a dollar was 20.67 per ounce, $100 could be exchanged for 4.84 ounces of gold.
Here's all the denominations issued by the Federal Reserve back then:
 This instrument was the facilitator of the Great depression, the inflation and deflation of the paper currency: as Thomas Jefferson warned long time ago:
This instrument was the facilitator of the Great depression, the inflation and deflation of the paper currency: as Thomas Jefferson warned long time ago:“If the American people ever allow private banks to control the issue of their currency first by inflation then by deflation the banks and corporations that will grow up around them will deprive the people of all property until their children wake up homeless on the continent their Fathers conquered... I believe that banking institutions are more dangerous to our liberties than standing armies... The issuing power should be taken from the banks and restored to the people to whom it properly belongs.”
THE CONFISCATION OF GOLD
The end of the dollar and the replacement of gold and gold certificates by Federal Reserve Notes worthless paper currency.
Executive Order 6102, issued on April 5, 1933, by President Franklin D. Roosevelt, forced everyone to exchange their gold and gold certificates for federal reserve notes at $20,67 FEDERAL RESERVE NOTES per ounce.
THIS WAS THE END OF THE DOLLAR. THE END OF THE GOLD STANDARD. THE END OF THE CONSTITUTIONAL REPUBLIC FORM OF GOVERNMENT. THE END OF FREEDOM. THE ABANDONMENT OF THE CONSTITUTIONAL PRINCIPLES.
The Gold Reserve Act of 1934
This act further devalued the "gold content of the FRNs" and ended the redemption of gold certificates for gold coins. One ounce of gold was now "35 FRNs" in theory but this was not entirely true.
Lets analice the evolution of the Federal Reserve Notes.
 Content of the contract:
Content of the contract:Federal reserve note
The United States of America
will pay to the bearer on demand: One hundred dollars
THIS NOTE IS LEGAL TENDER FOR ALL DEBTS, PUBLIC AND PRIVATE AND IT IS REDEEMABLE IN LAWFUL MONEY AT THE UNITED STATES TREASURY, OR AT ANY FEDERAL RESERVE BANK.
So if a dollar was 20.67 per ounce, $100 could be exchanged for one hundred dollars of Lawful money?
They eliminated the gold clause from the contract. This contract is a lie, what is this redeemable for? U.S treasuries? Different denominations of FRNs? They changed the definition of lawful money. This was never money this was a broken contract and it gets obvious in the next series...
1963 Series
This series look like they did photoshop on the "payable to the bearer on demand" part that was below franklin in previous series.
Content of the contract now was
Federal reserve note
The United States of America
THIS NOTE IS LEGAL TENDER FOR ALL DEBTS, PUBLIC AND PRIVATE.
ONE HUNDRED DOLLARS
Conclusion
Between 1913 and 1928 the dollar was gradually replaced by Federal Reserve Notes until in 1934 the gold standard was definitively abandoned. From that time the Federal Reserve Note became the "new legal tender money" replacing the dollar and slowly replacing silver coins too until in 1965 silver was definitively abandoned.
IT IS NOT THAT THE DOLLAR WAS “BACKED” BY SILVER OR GOLD.
Gold and silver were such powerful money during the founding of the United States of America that the founding fathers declared that only gold or silver coins can be “money” in America. Since gold and silver coinage was heavy and inconvenient for a lot of transactions, they were stored in banks and a claim check was issued as a money substitute. People traded their coupons as money or “currency.” Currency is not money, but a money substitute. Redeemable currency must promise to pay a dollar equivalent in gold or silver money. Federal Reserve Notes (FRNs) make no such promises and are not “money.” A Federal Reserve Note is a debt obligation of the federal United States government, not “money.” The federal United States government and the U.S. Congress were not and have never been authorized by the Constitution for the united States of America to issue currency of any kind, but only lawful money – gold and silver coin.
It is essential that we comprehend the distinction between real money and paper money substitute. One cannot get rich by accumulating money substitutes; one can only get deeper into debt. We the People no longer have any “money.” Most Americans have not been paid any “money” for a very long time, perhaps not in their entire life. Now do you comprehend why you feel broke? Now do you understand why you are “bankrupt” along with the rest of the country?
-
 @ 2ed3596e:98b4cc78
2025-05-01 17:01:26
@ 2ed3596e:98b4cc78
2025-05-01 17:01:26Our bounty program rewards Bitcoin Well Affiliates for making tutorials and Bitcoin Well walkthroughs. Make a video within our guidelines, share your post URLs (Youtube and X) and get paid over per video.
Each month we’ll have new bounty tasks with different tutorials available for you to make and earn sats. Click here to submit a Bitcoin Well bounty.
Bounty tasks and requirements for May 2025
For the month of May, the following bounty tasks will be available to approved Bitcoin Well Affiliates:
-
Buy bitcoin on-chain (Canada) – 63,000 sats
-
Requirements:
-
Buy walkthrough process: homescreen → buy page → e-transfer Q&A explained → review order → on-chain delivery explanation
-
Voice over guiding through each step
-
Mention OTC for Large purchases over $100k. Mention and include booking link in video description
-
Include affiliate webpage/referral link in video description
-
Uploaded to youtube and X/Nostr
-
-
Buy bitcoin via Lightning (USA) – 63,000 sats
-
Requirements:
-
Buy walkthrough process: homescreen → buy page → order form → bank funding and rate lock → order delivery expectations → confirm order
-
Voice over guiding through each step
-
Mention OTC for Large purchases over $100k. Mention and include booking link in video description
-
Include affiliate webpage/referral link in video description
-
Uploaded to youtube and X/Nostr
-
-
Pay bills on-chain (Canada) – 42,000 sats
-
Requirements:
-
Bill pay walkthrough process: homescreen → bill page → add a bill → bill pay order form → explain static bill pay address → confirm and review order → time to fulfill
-
Voice over guiding through each step
-
Include affiliate webpage/referral link in video description
-
Uploaded to youtube and X/Nostr
-
-
Recurring bitcoin buy (USA) – 105,000 sats
-
Requirements:
-
Recurring Buy walkthrough process: homescreen → buy page → order form → funding → date and frequency selection → order delivery expectations → confirm order
-
Voice over guiding through each step
-
Mention OTC for Large purchases over $100k. Mention and include booking link in video description
-
Include affiliate webpage/referral link in video description
-
Uploaded to youtube and X/Nostr
-
Please note that all requirements must be satisfied for a video to earn its bounty. Any questions about Bitcoin Well products details or bounty requirements can be directed to Konrad, Community Manager @ Bitcoin Well: k.fitz@bitcoinwell.com
Completed your bounty content and ready to earn your sats? Submit your bounty tasks here.
-
-
 @ 79dff8f8:946764e3
2025-05-01 16:48:55
@ 79dff8f8:946764e3
2025-05-01 16:48:55Hello world
-
 @ e968e50b:db2a803a
2025-05-01 16:46:13
@ e968e50b:db2a803a
2025-05-01 16:46:13Hey, are you familiar those scammy sites that will pay you to review companies? The line goes something like, "work from home and review products." Of course, the person is reviewing something online that they might not otherwise care about. When I look for reviews of a company, I'm almost always going to peer to peer type services.
Let's pause for a second for a seeming non-sequitur. Long story short, phone provider that I left has been charging me for an iPad that I accidentally didn't take off the plan. That's not the problem. The problem is that they made it IMPOSSIBLE to cancel this service, including going into a brick and mortar store. I'll spare you the details, but it took more than a full days work to get this thing cancelled. It was obvious that I wasn't even using the service, and it still cost me over a hundred bucks to square up after wasting so much of my life trying to get this thing cancelled on my account that supposedly didn't exist anymore.
Why is this relevant? I'm about to absolutely carpet bomb this company with bad reviews. They legitimately put significantly more work into trying to continue to charge me for this service I didn't want, didn't need, and didn't use, than they ever did trying to give me good service as a customer. When I started looking around online, I found a positive review I did about a flooring company two years ago...and wow! This review had so many great reviews. Beyond being amusingly recursive, it's real bad news for this phone company. I'm like a reviewing celebrity on this medium.
So...it occurred to me, what about a Trustpilot, BBB, or Angie's List type service that is fused with the sn news model? Put some skin in the game to review and put some skin in the game to endorse that review. stacker.reviews maybe?
Obviously, downzapping might not make sense there. Any company with a bad review could really hide their dirty laundry. But if they wanted to boost their good posts, plenty of safety mechanisms might make that costly (percentage of zaps going to website and boosts favored by numbers of zaps). I almost thought a review territory might make sense, but something like this would obviously need to be organized differently than a bulletin board.
I can imagine this being a good way to onboard people to bitcoin. Imagine it:
Wait, I can get some of these satoshi things for shouting to the rooftops about that plumber that saved my family's house?!? Hold my beer.
Wait, I can actually invest in this great review that warns people about that electrician?!?! Hold my warm beer.
idk Just a thought. I'm probably not the first person to think of this. Does it already exist? I got a humdinger of a harangue for it if so.
originally posted at https://stacker.news/items/968624
-
 @ d34e832d:383f78d0
2025-04-25 07:09:36
@ d34e832d:383f78d0
2025-04-25 07:09:361. Premise
The demand for high-capacity hard drives has grown exponentially with the expansion of cloud storage, big data, and personal backups. As failure of a storage device can result in significant data loss and downtime, understanding long-term drive reliability is critical. This research seeks to determine the most reliable manufacturer of 10TB+ HDDs by analyzing cumulative drive failure data over ten years from Backblaze, a leader in cloud backup services.
2. Methodology
Data from Backblaze, representing 350,000+ deployed drives, was analyzed to calculate the AFR of 10TB+ models from Seagate, Western Digital (including HGST), and Toshiba. AFR was calculated using cumulative data to reduce volatility and better illustrate long-term reliability trends. Power-on hours were used as the temporal metric to more accurately capture usage-based wear, as opposed to calendar-based aging.
3. Results and Analysis
3.1 Western Digital (including HGST)
- Ultrastar HC530 & HC550 (14TB & 16TB)
- AFR consistently below 0.35% after the initial “burn-in” period.
- Exhibited superior long-term stability.
- HGST Ultrastar HC520 (12TB)
- Demonstrated robust performance with AFR consistently under 0.5%.
- Excellent aging profile after year one.
3.2 Toshiba
- General Performance
- Noted for higher early failure rates (DOA issues), indicating manufacturing or transport inconsistencies.
- After stabilization, most models showed AFRs under 1%, which is within acceptable industry standards.
- Model Variability
- Differences in AFR observed between 4Kn and 512e sector models, suggesting firmware or controller differences may influence longevity.
3.3 Seagate
- Older Models (e.g., Exos X12)
- AFRs often exceeded 1.5%, raising concerns for long-term use in mission-critical applications.
- Newer Models (e.g., Exos X16)
- Improvements seen, with AFRs around 1%, though still higher than WD and HGST counterparts.
- Seagate’s aggressive pricing often makes these drives more attractive for cost-sensitive deployments.
4. Points Drawn
The data reveals a compelling narrative in brand-level reliability trends among high-capacity hard drives. Western Digital, especially through its HGST-derived Ultrastar product lines, consistently demonstrates superior reliability, maintaining exceptionally low Annualized Failure Rates (AFRs) and excellent operational stability across extended use periods. This positions WD as the most dependable option for enterprise-grade and mission-critical storage environments. Toshiba, despite a tendency toward higher early failure rates—often manifesting as Dead-on-Arrival (DOA) units—generally stabilizes to acceptable AFR levels below 1% over time. This indicates potential suitability in deployments where early failure screening and redundancy planning are feasible. In contrast, Seagate’s performance is notably variable. While earlier models displayed higher AFRs, more recent iterations such as the Exos X16 series have shown marked improvement. Nevertheless, Seagate drives continue to exhibit greater fluctuation in reliability outcomes. Their comparatively lower cost structure, however, may render them an attractive option in cost-sensitive or non-critical storage environments, where performance variability is an acceptable trade-off.
It’s crucial to remember that AFR is a probabilistic measure; individual drive failures are still possible regardless of brand or model. Furthermore, newer drive models need additional longitudinal data to confirm their long-term reliability.
5. Consider
Best Overall Choice: Western Digital Ultrastar HC530/HC550
These drives combine top-tier reliability (AFR < 0.35%), mature firmware, and consistent manufacturing quality, making them ideal for enterprise and archival use.Runner-Up (Budget Consideration): Seagate Exos X16
While reliability is slightly lower (AFR ~1%), the Exos series offers excellent value, especially for bulk storage.Cautionary Choice: Toshiba 10TB+ Models
Users should be prepared for potential early failures and may consider pre-deployment burn-in testing.
6. Recommendations for Buyers
- For mission-critical environments: Choose Western Digital Ultrastar models.
- For budget-focused or secondary storage: Seagate Exos offers acceptable risk-to-cost ratio.
- For experimental or non-essential deployments: Toshiba drives post-burn-in are serviceable.
7. Future Work
Based on publicly available Backblaze data, which reflects data center use and may not perfectly map to home or SMB environments. Sample sizes vary by model and may bias certain conclusions. Future research could integrate SMART data analytics, firmware version tracking, and consumer-use data to provide more granular insight.
References
- Backblaze. (2013–2023). Hard Drive Stats. Retrieved from https://www.backblaze.com/blog
- Manufacturer datasheets and reliability reports for Seagate, Western Digital, and Toshiba. -
 @ b00a728d:0c16788a
2025-05-01 15:46:13
@ b00a728d:0c16788a
2025-05-01 15:46:13Hey there, racing fans! Let’s talk about a straightforward betting strategy that’s been around for years, often used by folks who treat horse racing more like a business than a gamble. This method is all about following a clear staking plan to aim for a small, consistent profit per race—without needing to be a racing expert. I’ll break it down step-by-step so it’s easy to understand, even if you’re new to this! The Goal: Small, Steady Wins The idea here is to aim for a target profit (T) of 5 points per race. Think of a "point" as a unit of money you decide on—it could be $50, $1, or whatever you’re comfortable with. For example, I use a starting bank of $200, and I set each point at $1. So, 5 points = $5 profit per race. Important Rule: Once you pick the value of a point, stick with it throughout the entire betting sequence. Don’t change it, no matter what happens! Why This Works (Even If You Know Nothing About Racing) This plan is designed so that you’ll eventually win, even if you’re clueless about horses. The catch? You need to be patient and okay with small profits per point because the stakes (the amount you bet) can grow after each loss. For example: If you set each point at £1 and lose 10 races in a row, your 11th bet would need to recover $55 (your target plus losses).
If you set each point at 25p, you’d only need to recover $13.75 after 10 losses.
See the difference? Lower point values mean smaller risks, but also smaller profits. Pick a point value that matches the risk you’re willing to take and the profit you want to make. How the Staking Plan Works Here’s the basic idea: you start with a target profit of 5 points per race. If you lose, you add your loss to the next race’s target. If you win, you subtract your gain. The goal is to keep going until you hit your total profit target, then start over. Let’s break down the key terms: T (Target): Your profit goal for the race (starts at 5 points).
T + L: Your target plus any losses from previous races (or minus any gains if you won).
S (Stake): How much you bet on the race.
R (Result): Whether you won (e.g., 2-1 means the horse paid 2-to-1 odds) or lost (L).
W (Points Won): How many points you gained from a win.
L (Points Lost): How many points you lost from a bet.
AWL (Running Total): Your accumulated wins and losses over the sequence.
Once you reach your overall profit goal (like 40 points in the example below), you take your winnings and start the sequence over with a 5-point target. Example Sequence: Watch It in Action Here’s a sample sequence to show how this plays out. I’m using a 1-per-point value for simplicity: Race( see image posted for details in url or comment section)
What happened here? In Race 1, I aimed for 5 points but lost my 2-point stake, so my running total is -2.
In Race 2, I added my loss (2) to the new target (10), so I’m aiming for 12 points. I lost again, so my running total drops to -6.
By Race 8, I finally hit a big win (4-1 odds), gaining 44 points. My running total jumps to +50, which exceeds my overall target of 40 points.
I take my profit ($50 if each point is $1) and start over in Race 9 with a 5-point target.
How to Calculate Your Stake To figure out how much to bet (your stake), take your T + L (target plus losses) and divide by 3, rounding to the nearest whole number. Why 3? Because you want to bet on horses with odds of 3-1 or higher. A win at those odds will cover all your losses and give you your target profit. For example: In Race 4, my T + L is 33. Divide by 3: 33 ÷ 3 = 11. So, I bet 11 points.
My horse wins at 2-1 odds, so I get 22 points back (11 × 2). This clears my losses and gives me a profit.
Pro Tip: Stick to odds of evens (1-1) or higher. Many pros avoid “odds-on” bets (like 1-2) because they don’t pay enough to make this system work well. Tips to Make This Work for You Pick Your Races Wisely: You don’t have to bet on every race. Some pros bet on every race at a meeting (e.g., 6 races a day, 36 bets a week), but I recommend being selective. Consider using a professional tipping service for better picks—newspaper tips can be risky (one “expert” once picked 30 losers in a row!).
Spread Your Bets: Use 3 or 4 different bookmakers. No single bookie will be happy if you keep winning over time.
Account for Betting Tax (If Applicable): If there’s a tax on your bets, add it to your next race’s target. This way, the system covers the tax for you.
Be Prepared for Losing Streaks: Even with careful picks, you might hit a string of losses. That’s why you keep your point value low—so your stakes don’t balloon too much.
Why This Is a “Business,” Not Gambling People who use this method don’t see it as gambling—they treat racing like a business. The key is patience and discipline. A single win at 3-1 odds or higher will wipe out all your losses and deliver your target profit. It’s a slow grind, but it’s designed to keep you in the game long-term. Final Thoughts This staking plan is all about consistency and managing risk. Start with a small bank (like $200), set a point value you’re comfortable with (like 50 or 1), and stick to the rules. You don’t need to be a racing genius—just follow the system, bet smart, and wait for that big win to clear your slate and put profit in your pocket. Got questions or want to tweak this for your own style? Let me know, and I’ll help you fine-tune your approach! Happy betting!
originally posted at https://stacker.news/items/968545
-
 @ d34e832d:383f78d0
2025-04-25 06:06:32
@ d34e832d:383f78d0
2025-04-25 06:06:32This walkthrough examines the integration of these three tools as a combined financial instrument, focusing on their functionality, security benefits, and practical applications. Specter Desktop offers a user-friendly interface for managing Bitcoin wallets, Bitcoin Core provides a full node for transaction validation, and Coldcard provides the hardware security necessary to safeguard private keys. Together, these tools offer a robust and secure environment for managing Bitcoin holdings, protecting them from both online and physical threats.
We will explore their individual roles in Bitcoin management, how they can be integrated to offer a cohesive solution, and the installation and configuration process on OpenBSD. Additionally, security considerations and practical use cases will be addressed to demonstrate the advantages of this setup compared to alternative Bitcoin management solutions.
2.1 Specter Desktop
Specter Desktop is a Bitcoin wallet management software that provides a powerful, open-source interface for interacting with Bitcoin nodes. Built with an emphasis on multi-signature wallets and hardware wallet integration, Specter Desktop is designed to serve as an all-in-one solution for users who prioritize security and self-custody. It integrates seamlessly with Bitcoin Core and various hardware wallets, including Coldcard, and supports advanced features such as multi-signature wallets, which offer additional layers of security for managing Bitcoin funds.
2.2 Bitcoin Core
Bitcoin Core is the reference implementation of the Bitcoin protocol and serves as the backbone of the Bitcoin network. Running a Bitcoin Core full node provides users with the ability to independently verify all transactions and blocks on the network, ensuring trustless interaction with the blockchain. This is crucial for achieving full decentralization and autonomy, as Bitcoin Core ensures that users do not rely on third parties to confirm the validity of transactions. Furthermore, Bitcoin Core allows users to interact with the Bitcoin network via the command-line interface or a graphical user interface (GUI), offering flexibility in how one can participate in the Bitcoin ecosystem.
2.3 Coldcard
Coldcard is a Bitcoin hardware wallet that prioritizes security and privacy. It is designed to store private keys offline, away from any internet-connected devices, making it an essential tool for protecting Bitcoin holdings from online threats such as malware or hacking. Coldcard’s secure hardware environment ensures that private keys never leave the device, providing an air-gapped solution for cold storage. Its open-source firmware allows users to audit the wallet’s code and operations, ensuring that the device behaves exactly as expected.
2.4 Roles in Bitcoin Management
Each of these components plays a distinct yet complementary role in Bitcoin management:
- Specter Desktop: Acts as the interface for wallet management and multi-signature wallet configuration.
- Bitcoin Core: Provides a full node for transaction verification and interacts with the Bitcoin network.
- Coldcard: Safeguards private keys by storing them securely in hardware, providing offline signing capabilities for transactions.
Together, these tools offer a comprehensive and secure environment for managing Bitcoin funds.
3. Integration
3.1 How Specter Desktop, Bitcoin Core, and Coldcard Work Together
The integration of Specter Desktop, Bitcoin Core, and Coldcard offers a cohesive solution for managing and securing Bitcoin. Here's how these components interact:
- Bitcoin Core runs as a full node, providing a fully verified and trustless Bitcoin network. It validates all transactions and blocks independently.
- Specter Desktop communicates with Bitcoin Core to manage Bitcoin wallets, including setting up multi-signature wallets and connecting to hardware wallets like Coldcard.
- Coldcard is used to securely store the private keys for Bitcoin transactions. When a transaction is created in Specter Desktop, it is signed offline on the Coldcard device before being broadcasted to the Bitcoin network.
The main advantages of this setup include:
- Self-Sovereignty: By using Bitcoin Core and Coldcard, the user has complete control over their funds and does not rely on third-party services for transaction verification or key management.
- Enhanced Security: Coldcard provides the highest level of security for private keys, protecting them from online attacks and malware. Specter Desktop’s integration with Coldcard ensures a user-friendly method for interacting with the hardware wallet.
- Privacy: Using Bitcoin Core allows users to run their own full node, ensuring that they are not dependent on third-party servers, which could compromise privacy.
This integration, in combination with a user-friendly interface from Specter Desktop, allows Bitcoin holders to manage their funds securely, efficiently, and with full autonomy.
3.2 Advantages of This Setup
The combined use of Specter Desktop, Bitcoin Core, and Coldcard offers several advantages over alternative Bitcoin management solutions:
- Enhanced Security: The use of an air-gapped Coldcard wallet ensures private keys never leave the device, even when signing transactions. Coupled with Bitcoin Core’s full node validation, this setup offers unparalleled protection against online threats and attacks.
- Decentralization: Running a full Bitcoin Core node ensures that the user has full control over transaction validation, removing any dependence on centralized third-party services.
- User-Friendly Interface: Specter Desktop simplifies the management of multi-signature wallets and integrates seamlessly with Coldcard, making it accessible even to non-technical users.
4. Installation on OpenBSD
This section provides a step-by-step guide to installing Specter Desktop, Bitcoin Core, and setting up Coldcard on OpenBSD.
4.1 Installing Bitcoin Core
OpenBSD Bitcoin Core Build Guide
Updated for OpenBSD 7.6
This guide outlines the process of building Bitcoin Core (bitcoind), its command-line utilities, and the Bitcoin GUI (bitcoin-qt) on OpenBSD. It covers necessary dependencies, installation steps, and configuration details specific to OpenBSD.
Table of Contents
- Preparation
- Installing Required Dependencies
- Cloning the Bitcoin Core Repository
- Installing Optional Dependencies
- Wallet Dependencies
- GUI Dependencies
- Building Bitcoin Core
- Configuration
- Compilation
- Resource Limit Adjustments
1. Preparation
Before beginning the build process, ensure your system is up-to-date and that you have the necessary dependencies installed.
1.1 Installing Required Dependencies
As the root user, install the base dependencies required for building Bitcoin Core:
bash pkg_add git cmake boost libeventFor a complete list of all dependencies, refer to
dependencies.md.1.2 Cloning the Bitcoin Core Repository
Next, clone the official Bitcoin Core repository to a directory. All build commands will be executed from this directory.
bash git clone https://github.com/bitcoin/bitcoin.git1.3 Installing Optional Dependencies
Bitcoin Core supports optional dependencies for advanced functionality such as wallet support, GUI features, and notifications. Below are the details for the installation of optional dependencies.
1.3.1 Wallet Dependencies
While it is not necessary to build wallet functionality for running
bitcoindorbitcoin-qt, if you need wallet functionality:-
Descriptor Wallet Support: SQLite is required for descriptor wallet functionality.
bash pkg_add sqlite3 -
Legacy Wallet Support: BerkeleyDB is needed for legacy wallet support. It is recommended to use Berkeley DB 4.8. The BerkeleyDB library from OpenBSD ports cannot be used directly, so you will need to build it from source using the
dependsfolder.Run the following command to build it (adjust the path as necessary):
bash gmake -C depends NO_BOOST=1 NO_LIBEVENT=1 NO_QT=1 NO_ZMQ=1 NO_USDT=1After building BerkeleyDB, set the environment variable
BDB_PREFIXto point to the appropriate directory:bash export BDB_PREFIX="[path_to_berkeleydb]"
1.3.2 GUI Dependencies
Bitcoin Core includes a GUI built with Qt6. To compile the GUI, the following dependencies are required:
-
Qt6: Install the necessary parts of the Qt6 framework for GUI support.
bash pkg_add qt6-qtbase qt6-qttools -
libqrencode: The GUI can generate QR codes for addresses. To enable this feature, install
libqrencode:bash pkg_add libqrencodeIf you don't need QR encoding support, use the
-DWITH_QRENCODE=OFFoption during the configuration step to disable it.
1.3.3 Notification Dependencies
Bitcoin Core can provide notifications through ZeroMQ. If you require this functionality, install ZeroMQ:
bash pkg_add zeromq1.3.4 Test Suite Dependencies
Bitcoin Core includes a test suite for development and testing purposes. To run the test suite, you will need Python 3 and the ZeroMQ Python bindings:
bash pkg_add python py3-zmq
2. Building Bitcoin Core
Once all dependencies are installed, follow these steps to configure and compile Bitcoin Core.
2.1 Configuration
Bitcoin Core offers various configuration options. Below are two common setups:
-
Descriptor Wallet and GUI: Enables descriptor wallet support and the GUI. This requires SQLite and Qt6.
bash cmake -B build -DBUILD_GUI=ONTo see all available configuration options, run:
bash cmake -B build -LH -
Descriptor & Legacy Wallet, No GUI: Enables support for both descriptor and legacy wallets, but no GUI.
bash cmake -B build -DBerkeleyDB_INCLUDE_DIR:PATH="${BDB_PREFIX}/include" -DWITH_BDB=ON
2.2 Compile
After configuration, compile the project using the following command. Use the
-j Noption to parallelize the build process, whereNis the number of CPU cores you want to use.bash cmake --build buildTo run the test suite after building, use:
bash ctest --test-dir buildIf Python 3 is not installed, some tests may be skipped.
2.3 Resource Limit Adjustments
OpenBSD's default resource limits are quite restrictive and may cause build failures, especially due to memory issues. If you encounter memory-related errors, increase the data segment limit temporarily for the current shell session:
bash ulimit -d 3000000To make the change permanent for all users, modify the
datasize-curanddatasize-maxvalues in/etc/login.confand reboot the system.
Now Consider
By following these steps, you will be able to successfully build Bitcoin Core on OpenBSD 7.6. This guide covers the installation of essential and optional dependencies, configuration, and the compilation process. Make sure to adjust the resource limits if necessary, especially when dealing with larger codebases.
4.2 Installing Specter Desktop What To Consider
Specter Installation Guide for OpenBSD with Coldcard
This simply aims to provide OpenBSD users with a comprehensive and streamlined process for installing Specter, a Bitcoin wallet management tool. Tailored to those integrating Coldcard hardware wallets with Specter, this guide will help users navigate the installation process, considering various technical levels and preferences. Whether you're a beginner or an advanced user, the guide will empower you to make informed decisions about which installation method suits your needs best.
Specter Installation Methods on OpenBSD
Specter offers different installation methods to accommodate various technical skills and environments. Here, we explore each installation method in the context of OpenBSD, while considering integration with Coldcard for enhanced security in Bitcoin operations.
1. OS-Specific Installation on OpenBSD
Installing Specter directly from OpenBSD's packages or source is an excellent option for users who prefer system-native solutions. This method ensures that Specter integrates seamlessly with OpenBSD’s environment.
- Advantages:
- Easy Installation: Package managers (if available on OpenBSD) simplify the process.
- System Compatibility: Ensures that Specter works well with OpenBSD’s unique system configurations.
-
Convenience: Can be installed on the same machine that runs Bitcoin Core, offering an integrated solution for managing both Bitcoin Core and Coldcard.
-
Disadvantages:
- System-Specific Constraints: OpenBSD’s minimalistic approach might require manual adjustments, especially in terms of dependencies or running services.
-
Updates: You may need to manually update Specter if updates aren’t regularly packaged for OpenBSD.
-
Ideal Use Case: Ideal for users looking for a straightforward, system-native installation that integrates with the local Bitcoin node and uses the Coldcard hardware wallet.
2. PIP Installation on OpenBSD
For those comfortable working in Python environments, PIP installation offers a flexible approach for installing Specter.
- Advantages:
- Simplicity: If you’re already managing Python environments, PIP provides a straightforward and easy method for installation.
- Version Control: Gives users direct control over the version of Specter being installed.
-
Integration: Works well with any existing Python workflow.
-
Disadvantages:
- Python Dependency Management: OpenBSD users may face challenges when managing dependencies, as Python setups on OpenBSD can be non-standard.
-
Technical Knowledge: Requires familiarity with Python and pip, which may not be ideal for non-technical users.
-
Ideal Use Case: Suitable for Python-savvy users who already use Python-based workflows and need more granular control over their installations.
3. Docker Installation
If you're familiar with Docker, running Specter Desktop in Docker containers is a fantastic way to isolate the installation and avoid conflicts with the OpenBSD system.
- Advantages:
- Isolation: Docker ensures Specter runs in an isolated environment, reducing system conflicts.
- Portability: Once set up, Docker containers can be replicated across various platforms and devices.
-
Consistent Environment: Docker ensures consistency in the Specter installation, regardless of underlying OS differences.
-
Disadvantages:
- Docker Setup: OpenBSD’s Docker support isn’t as seamless as other operating systems, potentially requiring extra steps to get everything running.
-
Complexity: For users unfamiliar with Docker, the initial setup can be more challenging.
-
Ideal Use Case: Best for advanced users familiar with Docker environments who require a reproducible and isolated installation.
4. Manual Build from Source (Advanced Users)
For users looking for full control over the installation process, building Specter from source on OpenBSD offers the most flexibility.
- Advantages:
- Customization: You can customize Specter’s functionality and integrate it deeply into your system or workflow.
-
Control: Full control over the build and version management process.
-
Disadvantages:
- Complex Setup: Requires familiarity with development environments, build tools, and dependency management.
-
Time-Consuming: The process of building from source can take longer, especially on OpenBSD, which may lack certain automated build systems for Specter.
-
Ideal Use Case: Best for experienced developers who want to customize Specter to meet specific needs or integrate Coldcard with unique configurations.
5. Node-Specific Integrations (e.g., Raspiblitz, Umbrel, etc.)
If you’re using a Bitcoin node like Raspiblitz or Umbrel along with Specter, these node-specific integrations allow you to streamline wallet management directly from the node interface.
- Advantages:
- Seamless Integration: Integrates Specter directly into the node's wallet management system.
-
Efficient: Allows for efficient management of both Bitcoin Core and Coldcard in a unified environment.
-
Disadvantages:
- Platform Limitation: Not applicable to OpenBSD directly unless you're running a specific node on the same system.
-
Additional Hardware Requirements: Running a dedicated node requires extra hardware resources.
-
Ideal Use Case: Perfect for users already managing Bitcoin nodes with integrated Specter support and Coldcard hardware wallets.
6. Using Package Managers (Homebrew for Linux/macOS)
If you're running OpenBSD on a machine that also supports Homebrew, this method can simplify installation.
- Advantages:
- Simple Setup: Package managers like Homebrew streamline the installation process.
-
Automated Dependency Management: Handles all dependencies automatically, reducing setup complexity.
-
Disadvantages:
- Platform Limitation: Package managers like Homebrew are more commonly used on macOS and Linux, not on OpenBSD.
-
Version Control: May not offer the latest Specter version depending on the repository.
-
Ideal Use Case: Best for users with Homebrew installed, though it may be less relevant for OpenBSD users.
Installation Decision Tree for OpenBSD with Coldcard
- Do you prefer system-native installation or Docker?
- System-native (OpenBSD-specific packages) → Proceed to installation via OS package manager.
-
Docker → Set up Docker container for isolated Specter installation.
-
Are you comfortable with Python?
- Yes → Install using PIP for Python-based environments.
-
No → Move to direct installation methods like Docker or manual build.
-
Do you have a specific Bitcoin node to integrate with?
- Yes → Consider node-specific integrations like Raspiblitz or Umbrel.
- No → Install using Docker or manual source build.
Now Consider
When installing Specter on OpenBSD, consider factors such as your technical expertise, hardware resources, and the need for integration with Coldcard. Beginners might prefer simpler methods like OS-specific packages or Docker, while advanced users will benefit from building from source for complete control over the installation. Choose the method that best fits your environment to maximize your Bitcoin wallet management capabilities.
4.3 Setting Up Coldcard
Refer to the "Coldcard Setup Documentation" section for the installation and configuration instructions specific to Coldcard. At the end of writing.
5. Security Considerations
When using Specter Desktop, Bitcoin Core, and Coldcard together, users benefit from a layered security approach:
- Bitcoin Core offers transaction validation and network security, ensuring that all transactions are verified independently.
- Coldcard provides air-gapped hardware wallet functionality, ensuring private keys are never exposed to potentially compromised devices.
- Specter Desktop facilitates user-friendly management of multi-signature wallets while integrating the security of Bitcoin Core and Coldcard.
However, users must also be aware of potential security risks, including:
- Coldcard Physical Theft: If the Coldcard device is stolen, the attacker would need the PIN code to access the wallet, but physical security must always be maintained.
- Backup Security: Users must securely back up their Coldcard recovery seed to prevent loss of access to funds.
6. Use Cases and Practical Applications
The integration of Specter Desktop, Bitcoin Core, and Coldcard is especially beneficial for:
- High-Value Bitcoin Holders: Those managing large sums of Bitcoin can ensure top-tier security with a multi-signature wallet setup and Coldcard’s air-gapped security.
- Privacy-Conscious Users: Bitcoin Core allows for full network verification, preventing third-party servers from seeing transaction details.
- Cold Storage Solutions: For users who want to keep their Bitcoin safe long-term, the Coldcard provides a secure offline solution while still enabling easy access via Specter Desktop.
7. Coldcard Setup Documentation
This section should provide clear, step-by-step instructions for configuring and using the Coldcard hardware wallet, including how to pair it with Specter Desktop, set up multi-signature wallets, and perform basic operations like signing transactions.
8. Consider
The system you ant to adopt inculcates, integrating Specter Desktop, Bitcoin Core, and Coldcard provides a powerful, secure, and decentralized solution for managing Bitcoin. This setup not only prioritizes user privacy and security but also provides an intuitive interface for even non-technical users. The combination of full node validation, multi-signature support, and air-gapped hardware wallet storage ensures that Bitcoin holdings are protected from both online and physical threats.
As the Bitcoin landscape continues to evolve, this setup can serve as a robust model for self-sovereign financial management, with the potential for future developments to enhance security and usability.
-
 @ 40b9c85f:5e61b451
2025-04-24 15:27:02
@ 40b9c85f:5e61b451
2025-04-24 15:27:02Introduction
Data Vending Machines (DVMs) have emerged as a crucial component of the Nostr ecosystem, offering specialized computational services to clients across the network. As defined in NIP-90, DVMs operate on an apparently simple principle: "data in, data out." They provide a marketplace for data processing where users request specific jobs (like text translation, content recommendation, or AI text generation)
While DVMs have gained significant traction, the current specification faces challenges that hinder widespread adoption and consistent implementation. This article explores some ideas on how we can apply the reflection pattern, a well established approach in RPC systems, to address these challenges and improve the DVM ecosystem's clarity, consistency, and usability.
The Current State of DVMs: Challenges and Limitations
The NIP-90 specification provides a broad framework for DVMs, but this flexibility has led to several issues:
1. Inconsistent Implementation
As noted by hzrd149 in "DVMs were a mistake" every DVM implementation tends to expect inputs in slightly different formats, even while ostensibly following the same specification. For example, a translation request DVM might expect an event ID in one particular format, while an LLM service could expect a "prompt" input that's not even specified in NIP-90.
2. Fragmented Specifications
The DVM specification reserves a range of event kinds (5000-6000), each meant for different types of computational jobs. While creating sub-specifications for each job type is being explored as a possible solution for clarity, in a decentralized and permissionless landscape like Nostr, relying solely on specification enforcement won't be effective for creating a healthy ecosystem. A more comprehensible approach is needed that works with, rather than against, the open nature of the protocol.
3. Ambiguous API Interfaces
There's no standardized way for clients to discover what parameters a specific DVM accepts, which are required versus optional, or what output format to expect. This creates uncertainty and forces developers to rely on documentation outside the protocol itself, if such documentation exists at all.
The Reflection Pattern: A Solution from RPC Systems
The reflection pattern in RPC systems offers a compelling solution to many of these challenges. At its core, reflection enables servers to provide metadata about their available services, methods, and data types at runtime, allowing clients to dynamically discover and interact with the server's API.
In established RPC frameworks like gRPC, reflection serves as a self-describing mechanism where services expose their interface definitions and requirements. In MCP reflection is used to expose the capabilities of the server, such as tools, resources, and prompts. Clients can learn about available capabilities without prior knowledge, and systems can adapt to changes without requiring rebuilds or redeployments. This standardized introspection creates a unified way to query service metadata, making tools like
grpcurlpossible without requiring precompiled stubs.How Reflection Could Transform the DVM Specification
By incorporating reflection principles into the DVM specification, we could create a more coherent and predictable ecosystem. DVMs already implement some sort of reflection through the use of 'nip90params', which allow clients to discover some parameters, constraints, and features of the DVMs, such as whether they accept encryption, nutzaps, etc. However, this approach could be expanded to provide more comprehensive self-description capabilities.
1. Defined Lifecycle Phases
Similar to the Model Context Protocol (MCP), DVMs could benefit from a clear lifecycle consisting of an initialization phase and an operation phase. During initialization, the client and DVM would negotiate capabilities and exchange metadata, with the DVM providing a JSON schema containing its input requirements. nip-89 (or other) announcements can be used to bootstrap the discovery and negotiation process by providing the input schema directly. Then, during the operation phase, the client would interact with the DVM according to the negotiated schema and parameters.
2. Schema-Based Interactions
Rather than relying on rigid specifications for each job type, DVMs could self-advertise their schemas. This would allow clients to understand which parameters are required versus optional, what type validation should occur for inputs, what output formats to expect, and what payment flows are supported. By internalizing the input schema of the DVMs they wish to consume, clients gain clarity on how to interact effectively.
3. Capability Negotiation
Capability negotiation would enable DVMs to advertise their supported features, such as encryption methods, payment options, or specialized functionalities. This would allow clients to adjust their interaction approach based on the specific capabilities of each DVM they encounter.
Implementation Approach
While building DVMCP, I realized that the RPC reflection pattern used there could be beneficial for constructing DVMs in general. Since DVMs already follow an RPC style for their operation, and reflection is a natural extension of this approach, it could significantly enhance and clarify the DVM specification.
A reflection enhanced DVM protocol could work as follows: 1. Discovery: Clients discover DVMs through existing NIP-89 application handlers, input schemas could also be advertised in nip-89 announcements, making the second step unnecessary. 2. Schema Request: Clients request the DVM's input schema for the specific job type they're interested in 3. Validation: Clients validate their request against the provided schema before submission 4. Operation: The job proceeds through the standard NIP-90 flow, but with clearer expectations on both sides
Parallels with Other Protocols
This approach has proven successful in other contexts. The Model Context Protocol (MCP) implements a similar lifecycle with capability negotiation during initialization, allowing any client to communicate with any server as long as they adhere to the base protocol. MCP and DVM protocols share fundamental similarities, both aim to expose and consume computational resources through a JSON-RPC-like interface, albeit with specific differences.
gRPC's reflection service similarly allows clients to discover service definitions at runtime, enabling generic tools to work with any gRPC service without prior knowledge. In the REST API world, OpenAPI/Swagger specifications document interfaces in a way that makes them discoverable and testable.
DVMs would benefit from adopting these patterns while maintaining the decentralized, permissionless nature of Nostr.
Conclusion
I am not attempting to rewrite the DVM specification; rather, explore some ideas that could help the ecosystem improve incrementally, reducing fragmentation and making the ecosystem more comprehensible. By allowing DVMs to self describe their interfaces, we could maintain the flexibility that makes Nostr powerful while providing the structure needed for interoperability.
For developers building DVM clients or libraries, this approach would simplify consumption by providing clear expectations about inputs and outputs. For DVM operators, it would establish a standard way to communicate their service's requirements without relying on external documentation.
I am currently developing DVMCP following these patterns. Of course, DVMs and MCP servers have different details; MCP includes capabilities such as tools, resources, and prompts on the server side, as well as 'roots' and 'sampling' on the client side, creating a bidirectional way to consume capabilities. In contrast, DVMs typically function similarly to MCP tools, where you call a DVM with an input and receive an output, with each job type representing a different categorization of the work performed.
Without further ado, I hope this article has provided some insight into the potential benefits of applying the reflection pattern to the DVM specification.
-
 @ 0e67f053:cb1d4b93
2025-05-01 14:58:03
@ 0e67f053:cb1d4b93
2025-05-01 14:58:03By Carl Tuckerson, Host of “Feelings Before Finance”
Let’s be clear: May Day isn’t for mattress sales—it’s for smashing economic feudalism with a reusable water bottle and a union card.
Trump? Said he loved workers. Then he golfed while nurses rationed gloves. Elon Musk? Thinks labor laws are a nuisance between him and his next ego-fueled space tantrum. Meanwhile, AOC and Bernie are out here like revolutionary fairy godparents, yelling “TAX THE RICH” while sprinkling universal dignity on the masses.
May Day is for the tired. The overworked. The underpaid. And everyone who's ever been told “we’re a family” by a boss who’d fire them via Slack.
Today we rise. Together. Unionized. Moisturized. Ready to seize the means of basic decency.
✊ Happy May Day from Carl Tuckerson. And remember: No billionaire ever made a sandwich.
originally posted at https://stacker.news/items/968502
-
 @ c3ae4ad8:e54d46cb
2025-05-01 14:43:28
@ c3ae4ad8:e54d46cb
2025-05-01 14:43:28Ingredients
10 oz frozen chopped spinach, thawed 2 TB butter, divided ½ small shallot, minced 1/2 cup crumbled feta cheese 6 large or 9 medium eggs 1 cup of heavy cream salt & pepper
Directions
Preheat oven to 350F. Grease a pie dish with 1 tablespoon of the butter.
In a skillet, add butter and saute the diced shallots and cook until slightly softened.
Place the thawed chopped spinach into a towel or paper towel and wrap it around the spinach into a ball and squeeze until you remove as much liquid as possible.
In a large bowl, crack in the eggs and add the cream, salt & pepper, then whisk until foamy and increased in volume. Fluff up the spinach with a fork and add it to the egg mixture. Add the crumbled feta and fold both in.
In the greased pie dish, and then pour the egg mixture and bake at 350 for 35-40 minutes. Let cool for 10-15 minutes before serving.
Reheating and leftovers The best presentation and clean cuts will come from chilling for several hours or overnight in the fridge. To reheat, place a serving onto a microwave-safe plate and cover with a paper towel and heat for 30-40 seconds. It's also great cold.
Makes 6-8 servings.
-
 @ 2e8970de:63345c7a
2025-05-01 14:30:18
@ 2e8970de:63345c7a
2025-05-01 14:30:18Research out of China; they used ice lithography to fabricate 72 nm patterns on living tardigrades. The wild thing isn’t just that they “tattooed” tardigrades. It’s that tardigrades are so resilient, and focused electron beams so precise, that 40% of them survived and went about their lives after the procedure.
https://www.acs.org/pressroom/presspacs/2025/april/scientists-have-found-a-way-to-tattoo-tardigrades.html
originally posted at https://stacker.news/items/968469
-
 @ d34e832d:383f78d0
2025-04-24 07:22:54
@ d34e832d:383f78d0
2025-04-24 07:22:54Operation
This operational framework delineates a methodologically sound, open-source paradigm for the self-custody of Bitcoin, prominently utilizing Electrum, in conjunction with VeraCrypt-encrypted USB drives designed to effectively emulate the functionality of a cold storage hardware wallet.
The primary aim of this initiative is to empower individual users by providing a mechanism that is economically viable, resistant to coercive pressures, and entirely verifiable. This is achieved by harnessing the capabilities inherent in open-source software and adhering to stringent cryptographic protocols, thereby ensuring an uncompromising stance on Bitcoin sovereignty.
The proposed methodology signifies a substantial advancement over commercially available hardware wallets, as it facilitates the creation of a do-it-yourself air-gapped environment that not only bolsters resilience and privacy but also affirms the principles of decentralization intrinsic to the cryptocurrency ecosystem.
1. The Need For Trustless, Private, and Secure Storage
With Bitcoin adoption increasing globally, the need for trustless, private, and secure storage is critical. While hardware wallets like Trezor and Ledger offer some protection, they introduce proprietary code, closed ecosystems, and third-party risk. This Idea explores an alternative: using Electrum Wallet within an encrypted VeraCrypt volume on a USB flash drive, air-gapped via Tails OS or offline Linux systems.
2. Architecture of the DIY Hardware Wallet
2.1 Core Components
- Electrum Wallet (SegWit, offline mode)
- USB flash drive (≥ 8 GB)
- VeraCrypt encryption software
- Optional: Tails OS bootable environment
2.2 Drive Setup
- Format the USB drive and install VeraCrypt volumes.
- Choose AES + SHA-512 encryption for robust protection.
- Use FAT32 for wallet compatibility with Electrum (under 4GB).
- Enable Hidden Volume for plausible deniability under coercion.
3. Creating the Encrypted Environment
3.1 Initial Setup
- Download VeraCrypt from the official site; verify GPG signatures.
- Encrypt the flash drive and store a plain Electrum AppImage inside.
- Add a hidden encrypted volume with the wallet seed, encrypted QR backups, and optionally, a decoy wallet.
3.2 Mounting Workflow
- Always mount the VeraCrypt volume on an air-gapped computer, ideally booted into Tails OS.
- Never connect the encrypted USB to an internet-enabled system.
4. Air-Gapped Wallet Operations
4.1 Wallet Creation (Offline)
- Generate a new Electrum SegWit wallet inside the mounted VeraCrypt volume.
- Record the seed phrase on paper, or store it in a second hidden volume.
- Export xpub (public key) for use with online watch-only wallets.
4.2 Receiving Bitcoin
- Use watch-only Electrum wallet with the exported xpub on an online system.
- Generate receiving addresses without exposing private keys.
4.3 Sending Bitcoin
- Create unsigned transactions (PSBT) in the watch-only wallet.
- Transfer them via QR code or USB sneakernet to the air-gapped wallet.
- Sign offline using Electrum, then return the signed transaction to the online device for broadcast.
5. OpSec Best Practices
5.1 Physical and Logical Separation
- Use a dedicated machine or a clean Tails OS session every time.
- Keep the USB drive hidden and disconnected unless in use.
- Always dismount the VeraCrypt volume after operations.
5.2 Seed Phrase Security
- Never type the seed on an online machine.
- Consider splitting the seed using Shamir's Secret Sharing or metal backup plates.
5.3 Coercion Resilience
- Use VeraCrypt’s hidden volume feature to store real wallet data.
- Maintain a decoy wallet in the outer volume with nominal funds.
- Practice your recovery and access process until second nature.
6. Tradeoffs vs. Commercial Wallets
| Feature | DIY Electrum + VeraCrypt | Ledger/Trezor | |--------|--------------------------|---------------| | Open Source | ✅ Fully | ⚠️ Partially | | Air-gapped Usage | ✅ Yes | ⚠️ Limited | | Cost | 💸 Free (except USB) | 💰 $50–$250 | | Hidden/Coercion Defense | ✅ Hidden Volume | ❌ None | | QR Signing Support | ⚠️ Manual | ✅ Some models | | Complexity | 🧠 High | 🟢 Low | | Long-Term Resilience | ✅ No vendor risk | ⚠️ Vendor-dependent |
7. Consider
A DIY hardware wallet built with Electrum and VeraCrypt offers an unprecedented level of user-controlled sovereignty in Bitcoin storage. While the technical learning curve may deter casual users, those who value security, privacy, and independence will find this setup highly rewarding. This Operation demonstrates that true Bitcoin ownership requires not only control of private keys, but also a commitment to operational security and digital self-discipline. In a world of growing surveillance and digital coercion, such methods may not be optional—they may be essential.
8. References
- Nakamoto, Satoshi. Bitcoin: A Peer-to-Peer Electronic Cash System. 2008.
- Electrum Technologies GmbH. “Electrum Documentation.” electrum.org, 2024.
- VeraCrypt. “Documentation.” veracrypt.fr, 2025.
- Tails Project. “The Amnesic Incognito Live System (Tails).” tails.boum.org, 2025.
- Matonis, Jon. "DIY Cold Storage for Bitcoin." Forbes, 2014.
In Addition
🛡️ Create Your Own Secure Bitcoin Hardware Wallet: Electrum + VeraCrypt DIY Guide
Want maximum security for your Bitcoin without trusting third-party devices like Ledger or Trezor?
This guide shows you how to build your own "hardware wallet" using free open-source tools:
✅ Electrum Wallet + ✅ VeraCrypt Encrypted Flash Drive — No extra cost, no vendor risk.Let Go Further
What You’ll Need
- A USB flash drive (8GB minimum, 64-bit recommended)
- A clean computer (preferably old or dedicated offline)
- Internet connection (for setup only, then go air-gapped)
- VeraCrypt software (free, open-source)
- Electrum Bitcoin Wallet AppImage file
Step 1: Download and Verify VeraCrypt
- Go to VeraCrypt Official Website.
- Download the installer for your operating system.
- Verify the GPG signatures to ensure the download isn't tampered with.
👉 [Insert Screenshot Here: VeraCrypt download page]
Pro Tip: Never skip verification when dealing with encryption software!
Step 2: Download Electrum Wallet
- Go to Electrum Official Website.
- Download the Linux AppImage or Windows standalone executable.
- Again, verify the PGP signatures published on the site. 👉 [Insert Screenshot Here: Electrum download page]
Step 3: Prepare and Encrypt Your USB Drive
- Insert your USB drive into the computer.
- Open VeraCrypt and select Create Volume → Encrypt a Non-System Partition/Drive.
- Choose Standard Volume for now (later we'll talk about hidden volumes).
- Select your USB drive, set an extremely strong password (12+ random characters).
- For Encryption Algorithm, select AES and SHA-512 for Hash Algorithm.
- Choose FAT32 as the file system (compatible with Bitcoin wallet sizes under 4GB).
- Format and encrypt. 👉 [Insert Screenshot Here: VeraCrypt creating volume]
Important: This will wipe all existing data on the USB drive!
Step 4: Mount the Encrypted Drive
Whenever you want to use the wallet:
- Open VeraCrypt.
- Select a slot (e.g., Slot 1).
- Click Select Device, choose your USB.
- Enter your strong password and Mount. 👉 [Insert Screenshot Here: VeraCrypt mounted volume]
Step 5: Set Up Electrum in Offline Mode
- Mount your encrypted USB.
- Copy the Electrum AppImage (or EXE) onto the USB inside the encrypted partition.
- Run Electrum from there.
- Select Create New Wallet.
- Choose Standard Wallet → Create New Seed → SegWit.
- Write down your 12-word seed phrase on PAPER.
❌ Never type it into anything else. - Finish wallet creation and disconnect from internet immediately. 👉 [Insert Screenshot Here: Electrum setup screen]
Step 6: Make It Air-Gapped Forever
- Only ever access the encrypted USB on an offline machine.
- Never connect this device to the internet again.
- If possible, boot into Tails OS every time for maximum security.
Pro Tip: Tails OS leaves no trace on the host computer once shut down!
Step 7: (Optional) Set Up a Hidden Volume
For even stronger security:
- Repeat the VeraCrypt process to add a Hidden Volume inside your existing USB encryption.
- Store your real Electrum wallet in the hidden volume.
- Keep a decoy wallet with small amounts of Bitcoin in the outer volume.
👉 This way, if you're ever forced to reveal the password, you can give access to the decoy without exposing your true savings.
Step 8: Receiving Bitcoin
- Export your xpub (extended public key) from the air-gapped Electrum wallet.
- Import it into a watch-only Electrum wallet on your online computer.
- Generate receiving addresses without exposing your private keys.
Step 9: Spending Bitcoin (Safely)
To send Bitcoin later:
- Create a Partially Signed Bitcoin Transaction (PSBT) with the online watch-only wallet.
- Transfer the file (or QR code) offline (via USB or QR scanner).
- Sign the transaction offline with Electrum.
- Bring the signed file/QR back to the online device and broadcast it.
✅ Your private keys never touch the internet!
Step 10: Stay Vigilant
- Always dismount the encrypted drive after use.
- Store your seed phrase securely (preferably in a metal backup).
- Regularly practice recovery drills.
- Update Electrum and VeraCrypt only after verifying new downloads.
🎯 Consider
Building your own DIY Bitcoin hardware wallet might seem complex, but security is never accidental — it is intentional.
By using VeraCrypt encryption and Electrum offline, you control your Bitcoin in a sovereign, verifiable, and bulletproof way.⚡ Take full custody. No companies. No middlemen. Only freedom.
-
 @ f1989a96:bcaaf2c1
2025-05-01 15:50:38
@ f1989a96:bcaaf2c1
2025-05-01 15:50:38Good morning, readers!
This week, we bring pressing news from Belarus, where the regime’s central bank is preparing to launch its central bank digital currency in close collaboration with Russia by the end of 2026. Since rigging the 2020 election, President Alexander Lukashenko has ruled through brute force and used financial repression to crush civil society and political opposition. A Central Bank Digital Currency (CBDC) in the hands of such an authoritarian leader is a recipe for greater control over all aspects of financial activity.
Meanwhile, Russia is planning to further restrict Bitcoin access for ordinary citizens. This time, the Central Bank of Russia and the Ministry of Finance announced joint plans to launch a state-regulated cryptocurrency exchange available exclusively to “super-qualified investors.” Access would be limited to those meeting previously defined thresholds of $1.2 million in assets or an annual income above $580,000. This is a blatant attempt by the Kremlin to dampen the accessibility and impact of Bitcoin for those who need it most.
In freedom tech news, we spotlight Samiz. This new tool allows users to create a Bluetooth mesh network over nostr, allowing users' messages and posts to pass through nearby devices on the network even while offline. When a post reaches someone with an Internet connection, it is broadcast across the wider network. While early in development, Mesh networks like Samiz hold the potential to disseminate information posted by activists and human rights defenders even when authoritarian regimes in countries like Pakistan, Venezuela, or Burma try to restrict communications and the Internet.
We end with a reading of our very own Financial Freedom Report #67 on the Bitcoin Audible podcast, where host Guy Swann reads the latest news on plunging currencies, CBDCs, and new Bitcoin freedom tools. We encourage our readers to give it a listen and stay tuned for future readings of HRF’s Financial Freedom Report on Bitcoin Audible. We also include an interview with HRF’s global bitcoin adoption lead, Femi Longe, who shares insights on Bitcoin’s growing role as freedom money for those who need it most.
Now, let’s see what’s in store this week!
SUBSCRIBE HERE
GLOBAL NEWS
Belarus | Launching CBDC in Late 2026
Belarus is preparing to launch its CBDC, the digital ruble, into public circulation by late 2026. Roman Golovchenko, the chairman of the National Bank of the Republic of Belarus (and former prime minister), made the regime’s intent clear: “For the state, it is very important to be able to trace how digital money moves along the entire chain.” He added that Belarus was “closely cooperating with Russia regarding the development of the CBDC.” The level of surveillance and central control that the digital ruble would embed into Belarus’s financial system would pose existential threats to what remains of civil society in the country. Since stealing the 2020 election, Belarusian President Alexander Lukashenko has ruled through sheer force, detaining over 35,000 people, labeling dissidents and journalists as “extremists,” and freezing the bank accounts of those who challenge his authority. In this context, a CBDC would not be a modern financial tool — it would be a means of instant oppression, granting the regime real-time insight into every transaction and the ability to act on it directly.
Russia | Proposes Digital Asset Exchange Exclusively for Wealthy Investors
A month after proposing a framework that would restrict the trading of Bitcoin to only the country’s wealthiest individuals (Russians with over $1.2 million in assets or an annual income above $580,000), Russia’s Ministry of Finance and Central Bank have announced plans to launch a government-regulated cryptocurrency exchange available exclusively to “super-qualified investors.” Under the plan, only citizens meeting the previously stated wealth and income thresholds (which may be subject to change) would be allowed to trade digital assets on the platform. This would further entrench financial privilege for Russian oligarchs while cutting ordinary Russians off from alternative financial tools and the financial freedom they offer. Finance Minister Anton Siluanov claims this will bring digital asset operations “out of the shadows,” but in reality, it suppresses grassroots financial autonomy while exerting state control over who can access freedom money.
Cuba | Ecash Brings Offline Bitcoin Payments to Island Nation in the Dark
As daily blackouts and internet outages continue across Cuba, a new development is helping Cubans achieve financial freedom: Cashu ecash. Cashu is an ecash protocol — a form of digital cash backed by Bitcoin that enables private, everyday payments that can also be done offline — a powerful feature for Cubans experiencing up to 20-hour daily blackouts. However, ecash users must trust mints (servers operated by individuals or groups that issue and redeem ecash tokens) not to disappear with user funds. To leverage this freedom tech to its fullest, the Cuban Bitcoin community launched its own ecash mint, mint.cubabitcoin.org. This minimizes trust requirements for Cubans to transact with ecash and increases its accessibility by running the mint locally. Cuba Bitcoin also released a dedicated ecash resource page, helping expand accessibility to freedom through financial education. For an island nation where the currency has lost more than 90% of its value, citizens remain locked out of their savings, and remittances are often hijacked by the regime, tools like ecash empower Cubans to preserve their financial privacy, exchange value freely, and resist the financial repression that has left so many impoverished.
Zambia | Introduces Cyber Law to Track and Intercept Digital Communications
Zambia’s government passed two new cyber laws granting officials sweeping powers to track and intercept digital communications while increasing surveillance over Zambians' online activity. Officials insist it will help combat cybercrime. Really, it gives the president absolute control over the direction of a new surveillance agency — a powerful tool to crush dissent. This follows earlier plans to restrict the use of foreign currency in the economy to fight inflation, which effectively trapped Zambians in a financial system centered around the volatile “kwacha” currency (which reached a record low earlier this year with inflation above 16%). For activists, journalists, and everyday Zambians, the new laws over online activity threaten the ability to organize and speak freely while potentially hampering access to freedom tech.
India | Central Bank Deputy Governor Praises CBDC Capabilities
At the Bharat Inclusion Summit in Bengaluru, India, the deputy governor of the Reserve Bank of India (RBI), Rabi Sankar, declared, “I have so far not seen any use case that potentially can solve the problem of cross-border money transfer; only CBDC has the ability to solve it.” Yet — seemingly unbeknownst to Sankar, Bitcoin has served as an effective remittance tool for more than a decade at low cost, fast speed, and with no central point of control. Sankar’s remarks follow a growing push to normalize state-controlled, surveillance-based digital money as a natural progression of currency. The RBI’s digital rupee CBDC, currently in pilot phase, is quickly growing into one of the most advanced CBDCs on the planet. It is being embedded into the government’s UPI payment system and offered through existing financial institutions and platforms. Decentralized alternatives like Bitcoin can achieve financial inclusion and payment efficiency too — but without sacrificing privacy, autonomy, or basic rights over to the state.
Tanzania | Opposition Party Excluded From Election Amid Financial Repression
Last week, the Tanzanian regime banned the use of foreign currency in transactions, leaving Tanzanians to rely solely on the rapidly depreciating Tanzanian shilling. Now, Tanzania's ruling party has taken a decisive step to eliminate political opposition ahead of October’s general elections by barring the CHADEMA party from participation under the pretense of treason against their party leader, Tundu Lissu. Law enforcement arrested Lissu at a public rally where he was calling for electoral reforms. This political repression is not happening in isolation. Last year, the Tanzanian regime blocked access to X, detained hundreds of opposition members, and disappeared dissidents. These developments suggest a broader strategy to silence criticism and electoral competition through arrests, censorship, and economic coercion.
BITCOIN AND FREEDOM TECH NEWS
Samiz | Create a Bluetooth Mesh Network with Nostr
Samiz, an app for creating a Bluetooth mesh network over nostr, is officially available for testing. Mesh networks, where interconnected computers relay data to one another, can provide offline access to nostr if enough users participate. For example, when an individual is offline but has Samiz enabled, their device can connect to other nearby devices through Bluetooth, allowing nostr messages to hop locally from phone to phone until reaching someone with internet access, who can then broadcast the message to the wider nostr network. Mesh networks like this hold powerful implications for activists and communities facing censorship, Internet shutdowns, or surveillance. In places with restricted finances and organization, Samiz, while early in development, can potentially offer a way to distribute information through nostr without relying on infrastructure that authoritarian regimes can shut down.
Spark | New Bitcoin Payments Protocol Now Live
Lightspark, a company building on the Bitcoin Lightning Network, officially released Spark, a new payment protocol built on Bitcoin to make transactions faster, cheaper, and more privacy-protecting. Spark leverages a technology called statechains to enable self-custodial and off-chain Bitcoin transactions for users by transferring the private keys associated with their bitcoin rather than signing and sending a transaction with said keys. Spark also supports stablecoins (digital tokens pegged to fiat currency) and allows users to receive payments while offline. While these are promising developments, in its current state, Spark is not completely trustless; therefore, it is advisable only to hold a small balance of funds on the protocol as this new payment technology gets off the ground. You can learn more about Spark here.
Boltz | Now Supports Nostr Zaps
Boltz, a non-custodial bridge for swapping between different Bitcoin layers, released a new feature called Zap Swaps, enabling users to make Lightning payments as low as 21 satoshis (small units of bitcoin). This feature enables bitcoin microtransactions like nostr zaps, which are use cases that previously required workaround solutions. With the release, users of Boltz-powered Bitcoin wallets like Misty Breez can now leverage their wallets for zaps on nostr. These small, uncensorable bitcoin payments are a powerful tool for supporting activists, journalists, and dissidents — offering a permissionless way to support free speech and financial freedom worldwide. HRF is pleased to see this past HRF grantee add support for the latest freedom tech features.
Coinswap | Adds Support for Coin Selection
Coinswap, an in-development protocol that enables users to privately swap Bitcoin with one another, added support for coin selection, boosting the protocol’s privacy capabilities. Coin selection allows Bitcoin users to choose which of their unspent transaction outputs (UTXOs) to spend, giving them granular control over their transactions and the information they choose to reveal. For activists, journalists, and anyone operating under financial surveillance and repression, this addition (when fully implemented and released) can strengthen Bitcoin’s ability to resist censorship and protect human rights. HRF’s first Bitcoin Development Fund (BDF) grant was to Coinswap, and we are glad to see the continued development of the protocol.
bitcoin++ | Upcoming Bitcoin Developer Conference
The next bitcoin++ conference, a global, bitcoin-only developer series organized by Bitcoin educator Lisa Neigut, will occur in Austin, Texas, from May 7 to 9, 2025. A diverse group of privacy advocates, developers, and freedom tech enthusiasts will convene to learn about the mempool (the queue of pending and unconfirmed transactions in a Bitcoin node). Attendees will learn how Bitcoin transactions are sorted into blocks, mempool policies, and how transactions move through time and space to reach the next block. These events offer an incredible opportunity to connect with the technical Bitcoin community, who are ultimately many of the figures building the freedom tools that are helping individuals preserve their rights and freedoms in the face of censorship. Get your tickets here.
OpenSats | Announces 11th Wave of Nostr Grants
OpenSats, a nonprofit organization supporting open-source software and projects, announced its 11th round of grants for nostr, a decentralized protocol that enables uncensorable communications. Two projects stand out for their potential impact on financial freedom and activism: HAMSTR, which enables nostr messaging over ham radio that keeps information and payments flowing in off-grid or censored environments, and Nostr Double Ratchet, which brings end-to-end encrypted private messaging to nostr clients, safeguarding activists from surveillance. These tools help dissidents stay connected, coordinate securely, and transact privately, making them powerful assets for those resisting authoritarian control. Read the full list of grants here.
Bitcoin Design Community | Organizes Designathon for Open-Source UX Designers
The Bitcoin Design Community is hosting its next Designathon between May 4 and 18, 2025, inviting designers of all levels and backgrounds to creatively explore ideas to advance Bitcoin’s user experience and interface. Unlike traditional hackathons, this event centers specifically on design, encouraging open collaboration on projects that improve usability, accessibility, and innovation in open-source Bitcoin tools. Participants can earn monetary prizes, rewards, and recognition for their work. Anyone can join or start a project. Learn more here.
RECOMMENDED CONTENT
Plunging Currencies, CBDCs, and New Bitcoin Freedom Tools with Guy Swann
In this reading on the Bitcoin Audible podcast, host Guy Swan reads HRF’s Financial Freedom Report #67, offering listeners a front-row view into the latest developments in financial repression and resistance. He unpacks how collapsing currencies, rising inflation, and CBDC rollouts tighten state control in Turkey, Russia, and Nigeria. But he also highlights the tools for pushing back, from the first Stratum V2 mining pool to Cashu’s new Tap-to-Pay ecash feature. If you’re a reader of the Financial Freedom Report, we encourage you to check out the Bitcoin Audible podcast, where Guy Swan will be doing monthly readings of our newsletter. Listen to the full recording here.
Bitcoin Beyond Capital: Freedom Money for the Global South with Femi Longe
In this interview at the 2025 MIT Bitcoin Expo, journalist Frank Corva speaks with Femi Longe, HRF’s global bitcoin lead, who shares insights on Bitcoin’s growing role as freedom money for those living under authoritarian regimes. The conversation highlights the importance of building Bitcoin solutions that center on the specific problems faced by communities rather than the technology itself. Longe commends projects like Tando in Kenya and Bit.Spenda in Ghana, which integrate Bitcoin and Lightning into familiar financial channels, making Bitcoin more practical and accessible for everyday payments and saving. You can watch the interview here and catch the livestreams of the full 2025 MIT Bitcoin Expo here.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
-
 @ 7776c32d:45558888
2025-05-01 13:47:28
@ 7776c32d:45558888
2025-05-01 13:47:28I've edited this post to remove the spam. nostr:nevent1qvzqqqqqqypzqamkcvk5k8g730e2j6atadp6mxk7z4aaxc7cnwrlkclx79z4tzygqy88wumn8ghj7mn0wvhxcmmv9uq3jamnwvaz7tmswfjk66t4d5h8qunfd4skctnwv46z7qpqyrvezvufls3mrzc0att0vw0kw2pavu9pqlfzzrjtph5jrcnm28dqf26e23