-
 @ 7459d333:f207289b
2025-05-10 10:38:56
@ 7459d333:f207289b
2025-05-10 10:38:56Description: Just as Bitcoin enabled sovereignty over money, a decentralized shipping protocol would enable sovereignty over trade. An LN/Bisq inspired shipping protocol could create an unstoppable free market.
Bitcoin gave us monetary sovereignty, freeing us from central bank manipulation, inflation, and censorship. But there's a missing link in our freedom journey: the physical world of goods.
The Problem: Even with Bitcoin, global trade remains at the mercy of: - Arbitrary tariffs and import restrictions - Political censorship of goods - Privacy invasion of shipping information - Centralized shipping carriers
The Vision: A decentralized shipping protocol with these properties:
- "Onion-routed" packages: Each carrier only knows the previous and next hop
- Bitcoin-secured multi-sig escrow: Funds locked until package delivery confirmed
- Incentive alignment: Carriers set their own fees based on risk assessment
- Privacy tiers: Options for inspected vs. sealed packages with appropriate pricing
- End-to-end sovereignty: Sender and receiver maintain control, intermediate carriers just fulfill their role
How it could work:
- Sender creates shipping request with package details and destination
- Protocol finds optimal route through independent carriers
- Each hop secured by multi-sig deposits larger than package value
- Carriers only see next hop, not ultimate destination
- Reputation systems and economic incentives maintain integrity
This creates a free market where any individual can participate as a carrier, earning Bitcoin for facilitating trade. Just like Lightning Network nodes, anyone can open "channels" with trusted partners.
Impact: This would enable true free market principles globally, making artificial trade barriers obsolete and empowering individuals to engage in voluntary exchange regardless of geographic or political boundaries.
There are a lot of challenges. But the first question is if this is a real problem and if its worth solving it.
What components would need development first? How would you solve the physical handoff challenges?
originally posted at https://stacker.news/items/976326
-
 @ 3d073b19:4ae60f39
2025-05-10 21:51:32
@ 3d073b19:4ae60f39
2025-05-10 21:51:32Markdown test:
- italic
- bold in openletter
- Link: Nostr's current site
-
 @ 3d073b19:4ae60f39
2025-05-10 21:06:15
@ 3d073b19:4ae60f39
2025-05-10 21:06:15This is a test openletter
-
 @ 34f1ddab:2ca0cf7c
2025-05-10 21:03:11
@ 34f1ddab:2ca0cf7c
2025-05-10 21:03:11Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ c9badfea:610f861a
2025-05-10 18:57:30
@ c9badfea:610f861a
2025-05-10 18:57:30- Install Squircle (it's free and open source)
- Launch the app, tap the ⁞ icon and select Settings
- Configure your Git credentials as needed
- Add any remote servers under Cloud & Servers
- Return to the editor view and enjoy your mobile IDE
ℹ️ To clone a Git repository, tap ☰, long-press a directory in the file tree, and choose Clone
ℹ️ You may want to use it alongside Termux, a terminal emulator and Linux environment
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ c066aac5:6a41a034
2025-05-10 14:55:46
@ c066aac5:6a41a034
2025-05-10 14:55:46This is an article I wrote which originally appeared in the Pamphleteer, a publication run by a friend in Nashville. It has been edited from the published version, which I will link here for everyone to go check out the website and subscribe.
Step back fifty years in time with me if you will. A simpler time. You wake up in the house you could afford on a single income. Instead of blinding yourself with the light of your cell phone first thing in the morning, you wake up to make breakfast and coffee, your mind unencumbered by the stimulus of a thousand notifications. You can’t doom scroll (nor can you conceptualize what that even means).
You breathe in the moment, smelling your coffee with a deliberate, meditative inhale… As this brief moment of Nirvana passes, you decide to pick up the newspaper. You turn to page nine and see that Andy Kaufman, a comedian/performance artist you’ve seen on Taxi and Saturday Night Live, has declared himself “The Inter-Gender Wrestling Champion of the World.”
You are tempted to think this may be a joke, but suddenly you remember that you stepped back in time from the 21st century. You’re a modern person with evolved values. You ask yourself: is this an elaborate bit from Andy Kaufman, or was he simply ahead of his time? After all, you’re from the modern world where Imane Khelif is celebrated for his stunning and brave foray into women’s boxing (and where strangely, most news sources seem to deny that he’s a man).
All of a sudden, you abandon the bigotry of the past and invite Kaufman to come back with you to our present-day society. As you return to social media, endless notifications, a world full of stimulus, you ponder if Andy’s wrestling foray will be accepted for the beautiful thing that it is, rather than taken, without scrutiny, as a joke.
Exiting my narrative device now to speak to you directly: in the not-too-distant past, Andy Kaufman stepped into the ring and goaded women to wrestle with him. Back then, it was a bit. If such an act were to be replicated today, it would likely be celebrated and defended.
Inter-Gender sports pioneering aside, Kaufman's antics made Tennessee history; wrestling legend Jerry Lawler of Memphis went into the ring with Kaufman to relieve a female contestant and treated him to a Tennessee takedown.
Jerry invited the comedian to bring his act to Memphis. Leading up to the match, Kaufman relentlessly mocked his Southern audience, with jokes flexing his intelligence as "someone from Hollywood" and teaching Tennesseans how to use soap. After challenging a few women to wrestle, he was met with a famous Jerry Lawler Pilediver. This led to a staged feud between the two of them. The pair even reached the Letterman Show, with Kaufman in a neck brace.
As far as I know, Kaufman never identified as a woman. I don’t think he (or others from this period) could have fathomed the trans-sports drama occurring now. That said, there is something to be learned from his elaborate inter-gender wrestling bit: we’re watching the absurd unfold on the public stage. We should refuse to be gaslit and adopt Andy’s terminology and call this what it is: inter-gender sports. Whenever a biological man competes against a woman in any sporting event, we should all insist on letting everyone know that it is officially an inter-gender competition.
Maybe this modern dilemma could be solved if everyone surrounding these events treated the whole thing for what it was: an elaborate joke. Imagine if we treated it like WWE. The whole audience already knows it’s rigged anyway. Such rules of engagement would leave true biological women’s sports alone; it would keep their pride intact and be an assurance of physical protection.
That's the end of my original article. Just for fun, I wanted to add a response comment from my sister-in-law. She read the article and shared her thoughts with me, so I figured why not include them here.
I honestly believe mixed sports should be something that is encouraged more in our society—not because we should ignore biological differences and risks, especially in high-impact sports, but because normalizing this collaboration despite our different skill sets can strengthen women’s inclusivity not only as athletes, but in society as a whole. When I played mixed doubles in tennis and joined coed volleyball teams, I was pushed to improve and often held my own, even when the guys hit harder. And there are many sports like shooting, equestrian, archery, ect... that have nothing to do with “physical strength”. Training alongside men, whether in tennis, boxing, or volleyball, never has diminished my ability—it sharpened it, and that kind of mutual growth reflects a deeper value of inclusivity and respect that extends far beyond the sport. Thats my take! :)
-
 @ c9badfea:610f861a
2025-05-10 13:57:17
@ c9badfea:610f861a
2025-05-10 13:57:17- Install Grayjay (it's free and open source)
- Launch the app and navigate to the Sources tab
- Enable the desired sources (and log in if needed by tapping on the source and scrolling down to Authentication)
- Go to Android Settings > Apps, select Grayjay, and tap Open By Default and Add Link to automatically open supported links with Grayjay
- Enjoy
ℹ️ If you are using Obtainium to install apps, search for Grayjay on Complex Apps
-
 @ 6e64b83c:94102ee8
2025-05-05 16:50:13
@ 6e64b83c:94102ee8
2025-05-05 16:50:13Nostr-static is a powerful static site generator that transforms long-form Nostr content into beautiful, standalone websites. It makes your content accessible to everyone, even those not using Nostr clients. For more information check out my previous blog post How to Create a Blog Out of Nostr Long-Form Articles
What's New in Version 0.7?
RSS and Atom Feeds
Version 0.7 brings comprehensive feed support with both RSS and Atom formats. The system automatically generates feeds for your main content, individual profiles, and tag-specific pages. These feeds are seamlessly integrated into your site's header, making them easily discoverable by feed readers and content aggregators.
This feature bridges the gap between Nostr and traditional web publishing, allowing your content to reach readers who prefer feed readers or automated content distribution systems.
Smart Content Discovery
The new tag discovery system enhances your readers' experience by automatically finding and recommending relevant articles from the Nostr network. It works by:
- Analyzing the tags in your articles
- Fetching popular articles from Nostr that share these tags
- Using configurable weights to rank these articles based on:
- Engagement metrics (reactions, reposts, replies)
- Zap statistics (amount, unique zappers, average zap size)
- Content quality signals (report penalties)
This creates a dynamic "Recommended Articles" section that helps readers discover more content they might be interested in, all while staying within the Nostr ecosystem.
See the new features yourself by visiting our demo at: https://blog.nostrize.me
-
 @ c9badfea:610f861a
2025-05-10 11:08:51
@ c9badfea:610f861a
2025-05-10 11:08:51- Install FUTO Keyboard (it's free and open source)
- Launch the app, tap Switch Input Methods and select FUTO Keyboard
- For voice input, choose FUTO Keyboard (needs mic permission) and grant permission While Using The App
- Configure keyboard layouts under Languages & Models as needed
Adding Support for Non-English Languages
Voice Input
- Download voice input models from the FUTO Keyboard Add-Ons page
- For languages like Chinese, German, Spanish, Russian, French, Portuguese, Korean, and Japanese, download the Multilingual-74 model
- For other languages, download Multilingual-244
- Open FUTO Keyboard, go to Languages & Models, and import the downloaded model under Voice Input
Dictionaries
- Get dictionary files from AOSP Dictionaries
- Open FUTO Keyboard, navigate to Languages & Models, and import the dictionary under Dictionary
ℹ️ When typing, tap the microphone icon to use voice input
-
 @ c631e267:c2b78d3e
2025-05-10 09:50:45
@ c631e267:c2b78d3e
2025-05-10 09:50:45Information ohne Reflexion ist geistiger Flugsand. \ Ernst Reinhardt
Der lateinische Ausdruck «Quo vadis» als Frage nach einer Entwicklung oder Ausrichtung hat biblische Wurzeln. Er wird aber auch in unserer Alltagssprache verwendet, laut Duden meist als Ausdruck von Besorgnis oder Skepsis im Sinne von: «Wohin wird das führen?»
Der Sinn und Zweck von so mancher politischen Entscheidung erschließt sich heutzutage nicht mehr so leicht, und viele Trends können uns Sorge bereiten. Das sind einerseits sehr konkrete Themen wie die zunehmende Militarisierung und die geschichtsvergessene Kriegstreiberei in Europa, deren Feindbildpflege aktuell beim Gedenken an das Ende des Zweiten Weltkriegs beschämende Formen annimmt.
Auch das hohe Gut der Schweizer Neutralität scheint immer mehr in Gefahr. Die schleichende Bewegung der Eidgenossenschaft in Richtung NATO und damit weg von einer Vermittlerposition erhält auch durch den neuen Verteidigungsminister Anschub. Martin Pfister möchte eine stärkere Einbindung in die europäische Verteidigungsarchitektur, verwechselt bei der Argumentation jedoch Ursache und Wirkung.
Das Thema Gesundheit ist als Zugpferd für Geschäfte und Kontrolle offenbar schon zuverlässig etabliert. Die hauptsächlich privat finanzierte Weltgesundheitsorganisation (WHO) ist dabei durch ein Netzwerk von sogenannten «Collaborating Centres» sogar so weit in nationale Einrichtungen eingedrungen, dass man sich fragen kann, ob diese nicht von Genf aus gesteuert werden.
Das Schweizer Bundesamt für Gesundheit (BAG) übernimmt in dieser Funktion ebenso von der WHO definierte Aufgaben und Pflichten wie das deutsche Robert Koch-Institut (RKI). Gegen die Covid-«Impfung» für Schwangere, die das BAG empfiehlt, obwohl es fehlende wissenschaftliche Belege für deren Schutzwirkung einräumt, formiert sich im Tessin gerade Widerstand.
Unter dem Stichwort «Gesundheitssicherheit» werden uns die Bestrebungen verkauft, essenzielle Dienste mit einer biometrischen digitalen ID zu verknüpfen. Das dient dem Profit mit unseren Daten und führt im Ergebnis zum Verlust unserer demokratischen Freiheiten. Die deutsche elektronische Patientenakte (ePA) ist ein Element mit solchem Potenzial. Die Schweizer Bürger haben gerade ein Referendum gegen das revidierte E-ID-Gesetz erzwungen. In Thailand ist seit Anfang Mai für die Einreise eine «Digital Arrival Card» notwendig, die mit ihrer Gesundheitserklärung einen Impfpass «durch die Hintertür» befürchten lässt.
Der massive Blackout auf der iberischen Halbinsel hat vermehrt Fragen dazu aufgeworfen, wohin uns Klimawandel-Hysterie und «grüne» Energiepolitik führen werden. Meine Kollegin Wiltrud Schwetje ist dem nachgegangen und hat in mehreren Beiträgen darüber berichtet. Wenig überraschend führen interessante Spuren mal wieder zu internationalen Großbanken, Globalisten und zur EU-Kommission.
Zunehmend bedenklich ist aber ganz allgemein auch die manifestierte Spaltung unserer Gesellschaften. Angesichts der tiefen und sorgsam gepflegten Gräben fällt es inzwischen schwer, eine zukunftsfähige Perspektive zu erkennen. Umso begrüßenswerter sind Initiativen wie die Kölner Veranstaltungsreihe «Neue Visionen für die Zukunft». Diese möchte die Diskussionskultur reanimieren und dazu beitragen, dass Menschen wieder ohne Angst und ergebnisoffen über kontroverse Themen der Zeit sprechen.
Quo vadis – Wohin gehen wir also? Die Suche nach Orientierung in diesem vermeintlichen Chaos führt auch zur Reflexion über den eigenen Lebensweg. Das ist positiv insofern, als wir daraus Kraft schöpfen können. Ob derweil der neue Papst, dessen «Vorgänger» Petrus unsere Ausgangsfrage durch die christliche Legende zugeschrieben wird, dabei eine Rolle spielt, muss jede/r selbst wissen. Mir persönlich ist allein schon ein Führungsanspruch wie der des Petrusprimats der römisch-katholischen Kirche eher suspekt.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ a296b972:e5a7a2e8
2025-05-10 11:12:09
@ a296b972:e5a7a2e8
2025-05-10 11:12:09***Satiretüchtigkeit***
Deutschland hat den Satirikern den Krieg erklärt, in dem es Realitäten schafft, die die Phantasie der Autoren überbieten soll. Dazu hat das neu geschaffene Satireministerium die Satiretüchtigkeit ganz oben auf die Agenda gesetzt.
***Notlage***
Die Notlage in Deutschland ist in eine Notlage geraten. Das Ausrufen einer Notlage ist Gebot der Stunde, in der die Notlage der Notlage bekämpft werden kann.
***Grenzsicherung***
Nachdem als eine der ersten Amtshandlungen die deutschen Außengrenzen neu vermessen worden sind, hat sich herausgestellt, dass die Grenzen nur gesichert offenbleiben können. Der Bundesgrenzschutz hat ab sofort die Aufgabe übernommen, ausländisches CO2 an der Grenze aufzuhalten.
***Demokratiebeleidigungsparagraph***
Nach intensiver Recherche des Verfassungsschutzes hat sich herausgestellt, dass die Opposition die seinerzeitige Bundesregierung als „Diktatur“ und „totalitär“ bezeichnet hat. Das ist Demokratiebeleidigung. Ein neuer Paragraph ist bereits in der Ausarbeitung.
***Einhaltung des Koalitionsvertrags***
Aus gesicherten Quellen ist durchgesickert, dass der erste Bundeskanzler zweiter Wahl nun doch nicht sein Amt wahrnehmen will, weil das so nicht im Koalitionsvertrag steht. Schließlich halte man sich an selbigen und die Glaubwürdigkeit dürfe unter keinen Umständen infrage gestellt werden.
***Bundesamt für Fassungslosigkeit***
Das Bundesamt für Verfassungsschutz soll nach dem Willen der Bürger in Bundesamt für Fassungslosigkeit umbenannt werden. Es soll ein deutliches Zeichen gesetzt werden, dass Bürgerbeteiligung in Zukunft ein wichtiger Bestandteil der Politik sein wird.
***Brüssel – Zentrum Belgiens***
Der Bundeskanzler mit Blackrock-Hintergrund hat als eine seiner ersten Amtshandlungen die Neugestaltung des Finanzmarktes in Brüssel angeregt. Der Euro soll in den allermeisten Europäischen Staaten durch den Blackrock-Taler ersetzt werden.
***Salutokratie***
Die WHO hat größte Zustimmung bei der Einführung der Salutokratie erfahren. Die Europäer jubeln und ziehen zu Tausenden mit der EU-Fahne durch die europäischen Hauptstädte. Auf vielen Plakaten ist der folgende Text zu lesen: Die Pharmaindustrie ist ein wichtiger Wirtschaftszweig. Durch unsere Erkrankungen tragen wir einen wichtigen Teil dazu bei, dass sie zu unserem Wohle weiter forschen und neue Medikamente auf den Markt bringen kann.
***Elektronische Patientenakte***
Nach für die Ärzte verpflichtender Einführung der elektronischen Patientenakte konnten letzte Lücken in der Datenoffenheit beseitigt werden. Eine vollständige Transparenz ist jetzt für jedermann gewährleistet. Die Krankenkassen jubeln, weil Ferndiagnosen noch effizienter praktiziert werden können.
***Übermenschliche Leistungen***
Die neue Wirtschaftsministerin hat ihre eigene Messlatte sehr hoch angelegt. Sie will die übermenschlichen Leistungen ihres Vorgängers noch übermenschlicher übertreffen. Ihre Mitarbeiter arbeiten fieberhaft an einer neuen Wortschöpfung, die über den Begriff Übermenschlichkeit hinausgeht. Es ist größte Eile geboten, da eine Neuwahl der Regierung schon in den nächsten Monaten zu erwarten ist.
***Lieferprobleme***
Der brutale Umzug der ehemaligen Außen-Dings in die genderunfreundlichen USA verzögert sich, weil ein bekanntes Versandunternehmen die Lieferkette von feministischen Umzugskartons nicht nachweisen kann. Außerdem wurde von Lagerengpässen für die bevorstehende Auslieferung mobiler Toiletten nach Afrika berichtet.
***Erwischt***
Der ehemalige Corona-Minister II. wurde auf der Rückfahrt nach Berlin (1. Klasse, die ist noch pünktlich) dabei gesehen, wie er im Bistro-Wagen mit Genuss eine leicht versalzene Bockwurst gegessen hat. Nach Ankunft in Berlin musste der Vorrat an erlesenem, durstlöschendem Rotwein aufgefüllt werden.
***Verkauf aus Gewissensgründen***
Der Corona-Minister I. bekannt und berühmt geworden durch seine kaufmännisch geschickt eingefädelten Masken-Deals in bedarfsgerechter Anzahl, sucht derzeit nach einem Käufer für seine bescheidene Hütte in Hamburg, weil er mit dem Erlös den bankkaufmanntechnischen Gewinnüberhang ausgleichen will.
***Drohnennahverkehr***
Das zu verstaatlichende Staatsunternehmen Bahn will spätestens 2028 den Drohnennahverkehr im Halbstundentakt bundesweit einführen. In einer Pressekonferenz wurde bekannt, dass man mit den Logistikfragen im Umgang mit den angeschlossenen Glasfaserkabeln schon sehr große Fortschritte gemacht habe.
***Merz-Frisur***
Vollhaar-Inhaber in der CDU wollen sich zur Unterstützung und als Zeichen der Loyalität eine Merz-Frisur bei einem bekannten Star-Friseur schneiden lassen. Die Wartezeiten betragen derzeit rund 5 Tage. Die Friseur-Innung arbeitet an einem Schnellkurs: Merz-Frisur-tüchtig in drei Wochen!
***Bestsellerliste***
Die ehemalige Bundesmutti hat weitere Prosa in zwei Bänden angekündigt: Die Titel lauten „Einigkeit“ und „Recht“. Derzeit laufen die Maschinen der papierverarbeitenden Hygieneindustrie auf Hochtouren (gut für die Wirtschaft!), da die Bestellliste schon 1000 Seiten lang ist, die jedoch aufgrund der Gleichbehandlung nicht veröffentlicht werden kann.
***Autoindustrie mehrheitlich positiv***
Die Umsätze der deutschen Autoindustrie sollen angeblich um rund 30% eingebrochen sein. Das bedeutet, dass die Mehrheit, also rund 70% noch vorhanden ist, was für die Wirtschaft allgemein sehr gute Nachrichten sind. Außerdem können freie Kapazitäten jetzt zur Produktion von Tankfahrzeugen für Panzer genutzt werden.
***Unterbringungsprobleme gelöst***
Durch die anhaltende Insolvenzwelle deutscher Unternehmen werden Werkshallen frei, die in kürzester Zeit zu weltoffenen Unterkünften umgebaut werden. Erfahrungen aus der Plattenbauweise der ehemaligen DDR konnten hier erfolgreich eingesetzt werden.
***Pandemiebekämpfung***
Deutschland ist zepterhaltend in Präventionsmaßnahmen für zukünftig geplante Pandemien. Federführend soll das virenverseuchte Bargeld stufenweise abgeschafft werden. Ein neues Panik-Paper sieht bereits seiner gut durchdachten Vollendung entgegen.
***Verband der Schreib-Fachkräfte***
Der in Anlehnung des bekannten Satzes von Peter Scholl-Latour formulierte Satz: -Wer Begriffe wie „Kriegstüchtigkeit“ und „Hass und Hetze“ aus dunklen Zeiten verwendet, wird selbst zur dunklen Zeit-, wurde vom Verband der Schreib-Fachkräfte als umstritten eingeordnet.
***Leitkultur***
Experten für den unfallfreien Verzehr von Bananen haben in einer teleskopierten Studie herausgefunden, dass das Wort Leitkultur aus den Worten Leitkuh und Kultur künstlich in einem französischen Labor für Gain-of-Word-Forschung zusammengesetzt wurde. Beweis dafür ist das fehlende Ha, das so in der Natur nicht vorkommt. Der Laborsprung konnte so eindeutig nachgewiesen werden.
***Reformvorschlag***
Bisher galt: Alle Bürgerrechte sind Abwehrrechte gegen den Staat. In einer Ausschusstagung soll jetzt darüber befunden werden, ob diese Formulierung aus Gründen der Delegitimierung des Staates nicht geändert werden kann. Der Reformvorschlag lautet: In einer angestrebten Unseredemokratie soll die Hoheit über die Abwehrrechte der Bürger beim Staat liegen. In demokratischen Einzelverfahren soll darüber entschieden werden, wann und in welchem Umfang sie gegen die Bürger zur Anwendung kommen sollen.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ dc4152b3:dc737a27
2025-05-10 11:25:23
@ dc4152b3:dc737a27
2025-05-10 11:25:23181BET là một nền tảng trực tuyến nổi bật, cung cấp cho người dùng những trải nghiệm giải trí đa dạng và đầy sáng tạo. Với một giao diện thân thiện và dễ sử dụng, nền tảng này không chỉ hấp dẫn người tham gia nhờ vào tính năng dễ dàng tiếp cận mà còn bởi chất lượng dịch vụ vượt trội. Bằng cách tối ưu hóa trải nghiệm người dùng, 181BET đã nhanh chóng trở thành một trong những lựa chọn hàng đầu của những ai yêu thích các hoạt động giải trí trực tuyến. Nền tảng này cung cấp một loạt các trò chơi và hoạt động tương tác đa dạng, giúp người tham gia có thể thư giãn, giải trí và tận hưởng những giây phút thư thái. Các trò chơi được thiết kế một cách sáng tạo, kết hợp giữa tính giải trí cao và độ thử thách, tạo ra không gian thú vị cho người chơi. Bên cạnh đó, 181BET cũng chú trọng đến việc tạo ra một môi trường an toàn và bảo mật cao, giúp người dùng có thể hoàn toàn yên tâm khi tham gia vào các hoạt động giải trí trực tuyến mà không lo ngại về sự an toàn thông tin cá nhân hay giao dịch.
Điều làm nên sự khác biệt của 181BET chính là khả năng tạo ra một cộng đồng gắn kết và thân thiện, nơi mà người tham gia không chỉ có thể tham gia vào các trò chơi mà còn có thể giao lưu, kết nối và chia sẻ những khoảnh khắc vui vẻ. Nền tảng này cung cấp không chỉ những trò chơi đơn giản mà còn những hoạt động tương tác xã hội, giúp mọi người có thể giao lưu với nhau, học hỏi và tạo ra những mối quan hệ mới. Các tính năng giao lưu được thiết kế để mọi người có thể dễ dàng kết nối và chia sẻ với nhau, tạo ra một cộng đồng trực tuyến thân thiện và đầy sức sống. Mỗi thành viên có thể tham gia vào các hoạt động nhóm, trò chuyện và kết bạn với những người có cùng sở thích, từ đó xây dựng một mạng lưới bạn bè trực tuyến. Bên cạnh đó, 181BET còn cung cấp các tính năng nâng cao, giúp người dùng có thể dễ dàng theo dõi tiến trình và thành tích của mình trong các trò chơi, từ đó tạo động lực cho người tham gia tiếp tục khám phá và trải nghiệm những thử thách mới.
Ngoài những tính năng vượt trội về giải trí và kết nối cộng đồng, 181BET còn chú trọng đến việc bảo vệ quyền lợi và bảo mật cho người sử dụng. Nền tảng này sử dụng công nghệ bảo mật tiên tiến để đảm bảo rằng mọi thông tin cá nhân và giao dịch đều được bảo vệ một cách nghiêm ngặt. Các hệ thống mã hóa dữ liệu và bảo vệ thông tin giúp người dùng yên tâm tham gia vào các hoạt động mà không lo lắng về việc bị lộ thông tin cá nhân hay gặp phải các vấn đề bảo mật. Đặc biệt, 181BET luôn nỗ lực nâng cấp hệ thống bảo mật để phù hợp với các tiêu chuẩn cao nhất của ngành công nghệ hiện nay, tạo nên một môi trường giải trí trực tuyến an toàn và đáng tin cậy. Bên cạnh đó, nền tảng này còn cung cấp dịch vụ hỗ trợ khách hàng 24/7, sẵn sàng giải đáp mọi thắc mắc và giúp đỡ người tham gia trong suốt quá trình trải nghiệm. Với đội ngũ nhân viên hỗ trợ chuyên nghiệp và tận tâm, 181BET cam kết mang đến cho người dùng một trải nghiệm trực tuyến mượt mà và không gặp phải bất kỳ trở ngại nào. Sự kết hợp giữa công nghệ bảo mật hiện đại, dịch vụ hỗ trợ khách hàng tận tình và một nền tảng giải trí đa dạng đã giúp 181BET trở thành một lựa chọn lý tưởng cho những ai tìm kiếm một không gian giải trí trực tuyến chất lượng và an toàn.
-
 @ 57d1a264:69f1fee1
2025-05-10 05:45:52
@ 57d1a264:69f1fee1
2025-05-10 05:45:52Finale: once the industry-standard of music notation software, now a cautionary tale. In this video, I explore how it slowly lost its crown through decades of missed opportunities - eventually leading to creative collapse due to various bureaucratic intrigues, unforeseen technological changes and some of the jankiest UI/UX you've ever seen.
https://www.youtube.com/watch?v=Yqaon6YHzaU
originally posted at https://stacker.news/items/976219
-
 @ 6d8e2a24:5faaca4c
2025-05-10 08:11:36
@ 6d8e2a24:5faaca4c
2025-05-10 08:11:36
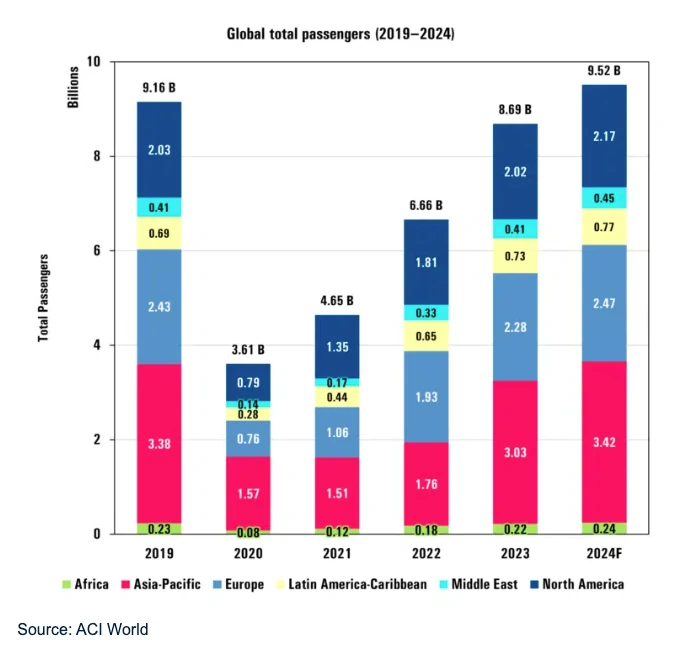
North American nations have been at the forefront of Bitcoin adoption; however, Nigeria, Kenya and South Africa have recently emerged as leaders in Africa.
There’s an increasing acceptance of Bitcoin on the African continent. More businesses, individuals and even financial organizations are using cryptocurrency to transact as an alternative to traditional banking systems. With the economies of the continent experiencing a lot of currency instability, poor banking infrastructure and exorbitantly priced remittances, Bitcoin is coming up as a viable solution financially. Analyzing Bitcoin price trends is crucial for investors, traders and businesses in Africa who want to implement digital assets in their operations.
The Impact of Bitcoin on the African Economy
North American nations have been at the forefront of Bitcoin adoption; however, Nigeria, Kenya and South Africa have recently emerged as leaders in Africa. Peer-to-peer cryptocurrency trading across the continent reached over $100 billion in 2023, making Africa one of the fastest-growing markets for blockchain technology, according to a report by Chainalysis. Several factors that fuel this growth include:
⚪ Less Dependable Fiat Currency : Zimbabwe and Nigeria have poor liquidity currencies, which makes it prudent for citizens to invest in Bitcoin to minimize losses due to devaluation over time.
⚪ Payments for Foreign Worker Remittances: Bitcoin is useful for relocating payments since it eliminates the need for using bitcoin remittance centers that charge ridiculous fees for payment processing.
⚪ Financial Inclusion : A large portion of the African population does not use banks. This makes bitcoin an ideal alternative, as it offers a decentralized and unbanked-friendly option for conducting transactions.
How Bitcoin’s Price Trends Affect the African Market
Businesses and individuals’ activities with bitcoin are directly proportional to its price trends and different nations have different ways through which they analyze this. Take Nigeria, for instance, where the e-commerce platform Patricia and several local sellers on Jumia have had to change their prices multiple times a day to keep in line with the fluctuating value of bitcoin. This has led to the platform’s volatility driving the pricing strategy of freelancers and remote workers who are paid in bitcoin and the currency has to be converted before being spent. As investor sentiment increases, so too does Bitcoin’s value, reaching 71,333 dollars in April of 2024, according to estimates from CoinMarketCap. The volatility, however, remains high and so there is a lot of uncertainty for African investors and businesses hoping to capitalize on the price movement.
Amongst the factors that impact the price movement of bitcoin, these are the most significant:
⚪ Global Adoption and Institutional Investments: An increase in spending by corporations leads to a higher demand and price for bitcoin.
⚪ Regulatory Changes : The law about cryptocurrency in different African countries is a vital influencer of regard and value for bitcoin.
⚪ Market Speculation and Trading Activity: The volatility of Bitcoin's price remains dependent on investor sentiment, especially in the emerging markets.
African Governments and Cryptocurrency Regulation
The policies for regulating Bitcoin are different in various countries in Africa. While countries like South Africa and Kenya are skeptical but working towards adjusting their policies to incorporate cryptocurrency into their economies, other nations remain hesitant. The following is a summary of the most important changes:
⚪ South Africa: The Financial Sector Conduct Authority (FSCA) offered more structured regulations by classifying crypto assets as financial products. This is a notable development towards more stringent regulations.
⚪ Nigeria: The Central Bank of Nigeria has previously restricted banks from supporting the facilitation of crypto transactions but is in the process of allowing it due to newly offered licenses to cryptocurrency exchanges, which under certain guidelines allow them to conduct regulated crypto activities.
⚪ Kenya: The Capital Markets Authority is seeking ways to regulate the security features of Bitcoin to enable it to reduce fraud. Bitcoin’s Impact on E-commerce and Small Businesses in Africa
With the rise of cryptocurrency acceptance, small-scale businesses and e-commerce businesses are increasing the option of paying for goods and services in Bitcoin. Businesses can reduce costs by:
⚪ Decreased Transaction Fees: Payments made using Bitcoin are usually cheaper than those made through credit cards. For example, some merchants in Ghana are beginning to use Bitcoin to bypass high fee payment processing, increase their profit margins and improve overall business profitability.
⚪ Reduced Transaction Delays: Banking transactions processed through the blockchain do away with delays associated with traditional banking.
⚪ Access to Global Markets: Businesses in Africa have no issues engaging with foreign clients because there is no currency conversion needed.
For instance, Yellow Card is a cryptocurrency exchange that operates in several countries in Africa and allows the trading of Bitcoins. In 2024, Yellow Card received more compliance approvals, which allowed the business to serve more than 20 countries in Africa. It now stands as a central player in the regional ecosystem of crypto. The platform allows businesses or individuals to transact efficiently with Bitcoin.
Challenges and Risks of Bitcoin Adoption in Africa
Unlike the advantages, there are several challenges regarding the adoption of Bitcoin in Africa:
⚪ Regulatory Uncertainty: The considerable flux of policies is difficult for businesses and investors to navigate, although some countries are beginning to put clearer policies into place, such as South Africa and Nigeria. As an example, Nigeria has plans to regulate the exchange of digital assets and put some control over it through the issuing of licenses for crypto exchanges, which are expected to be released in 2024.
⚪ Price Volatility: Changes in the price of Bitcoin can affect savings and transactions for businesses.
⚪ Limited Infrastructure: Internet and computer skills are primary requirements for greater acceptance.
Conclusion
Bitcoin is increasingly becoming a key component of Africa’s financial ecosystem by providing banking services or alternatives, facilitating financial remittances and supporting inclusion. Experts expect that Africa will increasingly adopt Bitcoin as a major tool of payment and remittance service across borders and for digital financial transactions. This will be the case if the regulations supporting its growth are put in place. While price volatility and regulatory challenges persist, knowing how prices behave and the developments within the Bitcoin ecosystem will help investors and businesses understand the new economy Africa is adopting. Africa indeed has the chance to use strategic adoption of technology to improve economic development and innovation through Bitcoin if action is taken.
2025Content from a Premium Partner InfoWire https://allafrica.com/stories/202503240689.html
-
 @ 57d1a264:69f1fee1
2025-05-10 05:34:46
@ 57d1a264:69f1fee1
2025-05-10 05:34:46
For generations before generative text, writers have used the em dash to hop between thoughts, emotions, and ideas. Dickens shaped his morality tales with it, Woolf’s stream-of-consciousness flowed through it, Kerouac let it drive his jazz-like prose. Today, Sally Rooney threads it through her quiet truths of the heart.
But this beloved punctuation mark has become a casualty of the algorithmic age. The em dash has been so widely adopted by AI-generated text that even when used by human hands, it begs the question: was this actually written or apathetically prompted?
The battle for the soul of writing is in full swing. And the human fightback starts here. With a new punctuation mark that serves as a symbol of real pondering, genuine daydreaming, and true editorial wordsmithery. Inspired by Descartes’ belief that thinking makes us human, the am dash is a small but powerful testament that the words you’ve painstakingly and poetically pulled together are unequivocally, certifiably, and delightfully your own.
Let's reclain writig from AI—oneam dash at time.
Download the fonts:
— Aereal https://bit.ly/3EO6fo8 — Times New Human https://bit.ly/4jQTcRS
Learn more about the am dash
https://www.theamdash.com
originally posted at https://stacker.news/items/976218
-
 @ 6e0ea5d6:0327f353
2025-05-04 14:53:42
@ 6e0ea5d6:0327f353
2025-05-04 14:53:42Amico mio, ascolta bene!
Without hesitation, the woman you attract with lies is not truly yours. Davvero, she is the temporary property of the illusion you’ve built to seduce her. And every illusion, sooner or later, crumbles.
Weak men sell inflated versions of themselves. They talk about what they don’t have, promise what they can’t sustain, adorn their empty selves with words that are nothing more than a coat of paint. And they do this thinking that, later, they’ll be able to "show who they really are." Fatal mistake, cazzo!
The truth, amico mio, is not something that appears at the end. It is what holds up the whole beginning.
The woman who approaches a lie may smile at first — but she is smiling at the theater, not at the actor. When the curtains fall, what she will see is not a man. It will be a character tired of performing, begging for love from a self-serving audience in the front row.
That’s why I always point out that lying to win a woman’s heart is the same as sabotaging your own nature. The woman who comes through an invented version of you will be the first to leave when the veil of lies tears apart. Not out of cruelty, but out of consistency with her own interest. Fine... She didn’t leave you, but rather, that version of yourself never truly existed to be left behind.
A worthy man presents himself without deceptive adornments. And those who stay, stay because they know exactly who they are choosing as a man. That’s what differentiates forged seduction from the convenience of love built on honor, loyalty, and respect.
Ah, amico mio, I remember well. It was lunch on an autumn day in Catania. Mediterranean heat, and the Nero D'Avola wine from midday clinging to the lips like dried blood. Sitting in the shade of a lemon tree planted right by my grandfather's vineyard entrance, my uncle — the oldest of my father’s brothers — spoke little, but when he called us to sit by his side, all the nephews would quiet down to listen. And in my youth, he told me something that has never left my mind.
“In Sicily, the woman who endures the silence of a man about his business is more loyal than the one who is enchanted by speeches about what he does or how much he earns. Perchè, figlio mio, the first one has seen the truth. The second one, only a false shine.”
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 57d1a264:69f1fee1
2025-05-10 05:11:27
@ 57d1a264:69f1fee1
2025-05-10 05:11:27Consider the following two charts from A History of Clojure which detail the introduction and retention of new code by release for both Clojure and for Scala.
While this doesn't necessarily translate to library stability, it's reasonable to assume that the attitude of the Clojure maintainers will seep into the community. And that assumption is true.
Consider a typical Javascript program. What is it comprised of? Objects, objects, and more objects. Members of those objects must be either introspected or divined. Worse, it's normal to monkeypatch those objects, so the object members may (or may not) change over time.
Now, consider a typical Clojure program. What is it comprised of? Namespaces. Those namespaces contain functions and data. Functions may be dynamically generated (via macros), but it is extremely rare to "monkeypatch" a namespace. If you want to know what functions are available in a namespace, you can simply read the source file.
Continue reading https://potetm.com/devtalk/stability-by-design.html
originally posted at https://stacker.news/items/976215
-
 @ d360efec:14907b5f
2025-05-10 03:57:17
@ d360efec:14907b5f
2025-05-10 03:57:17Disclaimer: * การวิเคราะห์นี้เป็นเพียงแนวทาง ไม่ใช่คำแนะนำในการซื้อขาย * การลงทุนมีความเสี่ยง ผู้ลงทุนควรตัดสินใจด้วยตนเอง
-
 @ fbf0e434:e1be6a39
2025-05-10 07:41:42
@ fbf0e434:e1be6a39
2025-05-10 07:41:42Hackathon 概要
Stellar Build Better Hackathon 已圆满落幕,共有 220 名注册开发者参与,84 个项目获得批准。本次活动旨在通过 Stellar 的智能合约推动实际应用,强调社区合作与技术进步。参赛者在三个类别中展开角逐,总奖金为 25000 美元的 USDC,类别包括:Better Finance、Better Creativity 和 Better Access。
开发者探索了 DeFi 可及性工具、跨境支付解决方案、创作者经济平台和身份解决方案等领域。Hackathon 为与全球开发者交流及知名加密公司曝光提供了契机。此外,还设有技术研讨会和现场 demo 环节,为参赛者提供支持。
在成果方面,一等奖 12,000 USDC 授予了提升金融可及性的项目。二、三等奖分别获得 8,000 和 5,000 USDC 的奖励,以表彰其在创意工具和可访问性解决方案方面的创新。通过这些奖励,此次活动凸显了 Stellar 在促进实用创新及扩展其生态系统中智能合约应用方面的作用。
Hackathon 获奖者
第一名
- PayZoll_Stellar - PayZoll 在 Stellar 生态系统中集成了AI和区块链,提供安全、自动化和透明的全球薪资服务,提升了薪资管理的效率和可靠性。
第二名
- StellarFinance - 该平台在Stellar区块链上促进用户与财务顾问之间的连接,提供专注于诚信和用户参与的安全透明的金融服务。
第三名
- Soroban to MCP Server in seconds + Policy Signers Playground - 此解决方案将Stellar Soroban智能合约转换为MCP服务器,实现自然语言交互,支持AI代理执行并增强智能合约功能。
前往 DoraHacks 查看参与hackathon的所有项目。
关于主办方
Stellar Development Foundation
Stellar Development Foundation 力求促进 Stellar 网络的增长和发展,这是一种旨在促进高效跨境交易的区块链平台。基金会专注于去中心化金融(DeFi),实施推进全球金融包容性的项目。通过与广泛的网络合作,该组织推广可扩展的区块链解决方案,确保金融服务的可及性和可靠性。其使命是通过创新的开源技术,为全球经济提供公平的通道。
-
 @ 266815e0:6cd408a5
2025-05-02 22:24:59
@ 266815e0:6cd408a5
2025-05-02 22:24:59Its been six long months of refactoring code and building out to the applesauce packages but the app is stable enough for another release.
This update is pretty much a full rewrite of the non-visible parts of the app. all the background services were either moved out to the applesauce packages or rewritten, the result is that noStrudel is a little faster and much more consistent with connections and publishing.
New layout
The app has a new layout now, it takes advantage of the full desktop screen and looks a little better than it did before.
Removed NIP-72 communities
The NIP-72 communities are no longer part of the app, if you want to continue using them there are still a few apps that support them ( like satellite.earth ) but noStrudel won't support them going forward.
The communities where interesting but ultimately proved too have some fundamental flaws, most notably that all posts had to be approved by a moderator. There were some good ideas on how to improve it but they would have only been patches and wouldn't have fixed the underlying issues.
I wont promise to build it into noStrudel, but NIP-29 (relay based groups) look a lot more promising and already have better moderation abilities then NIP-72 communities could ever have.
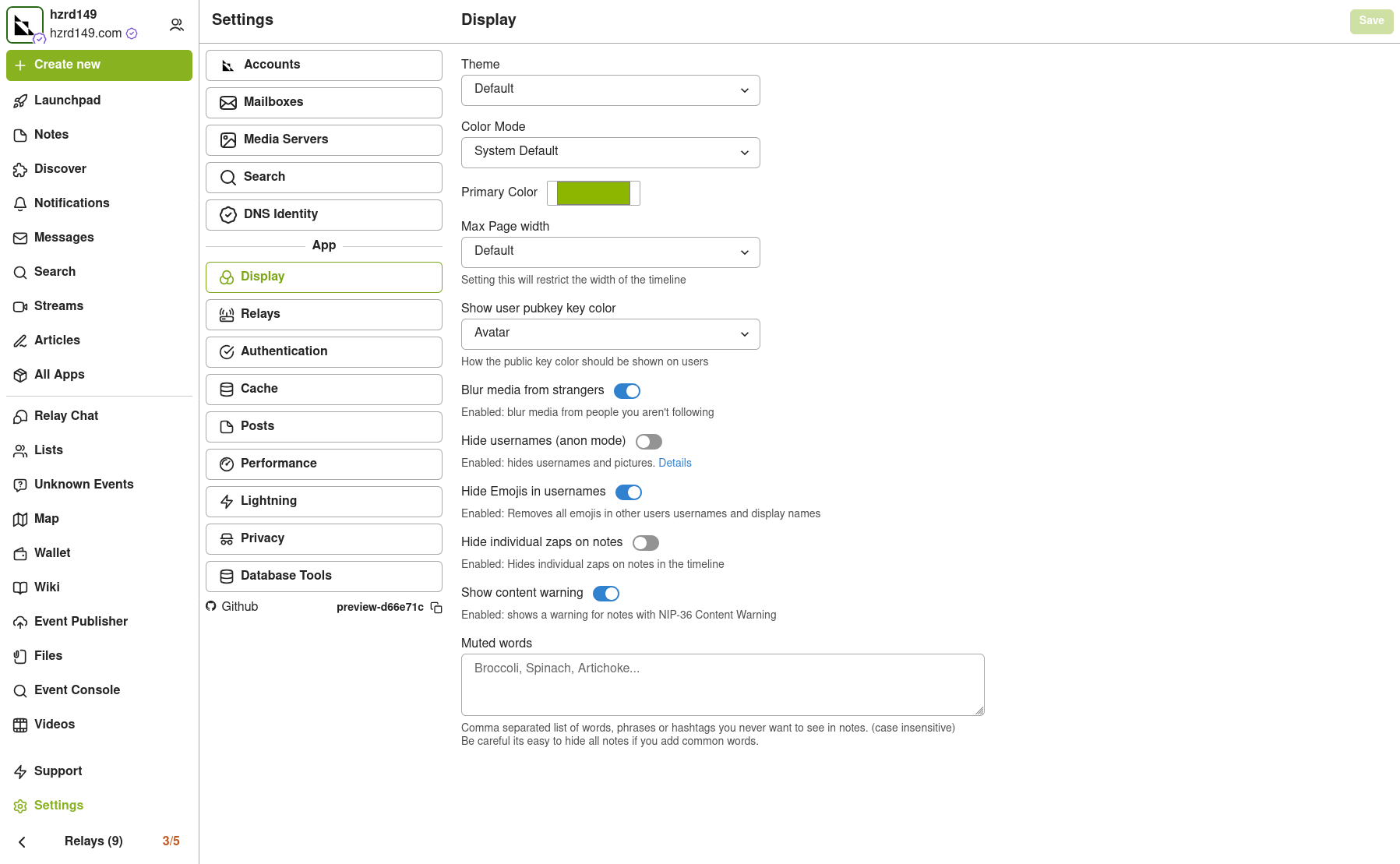
Settings view
There is now a dedicated settings view, so no more hunting around for where the relays are set or trying to find how to add another account. its all in one place now
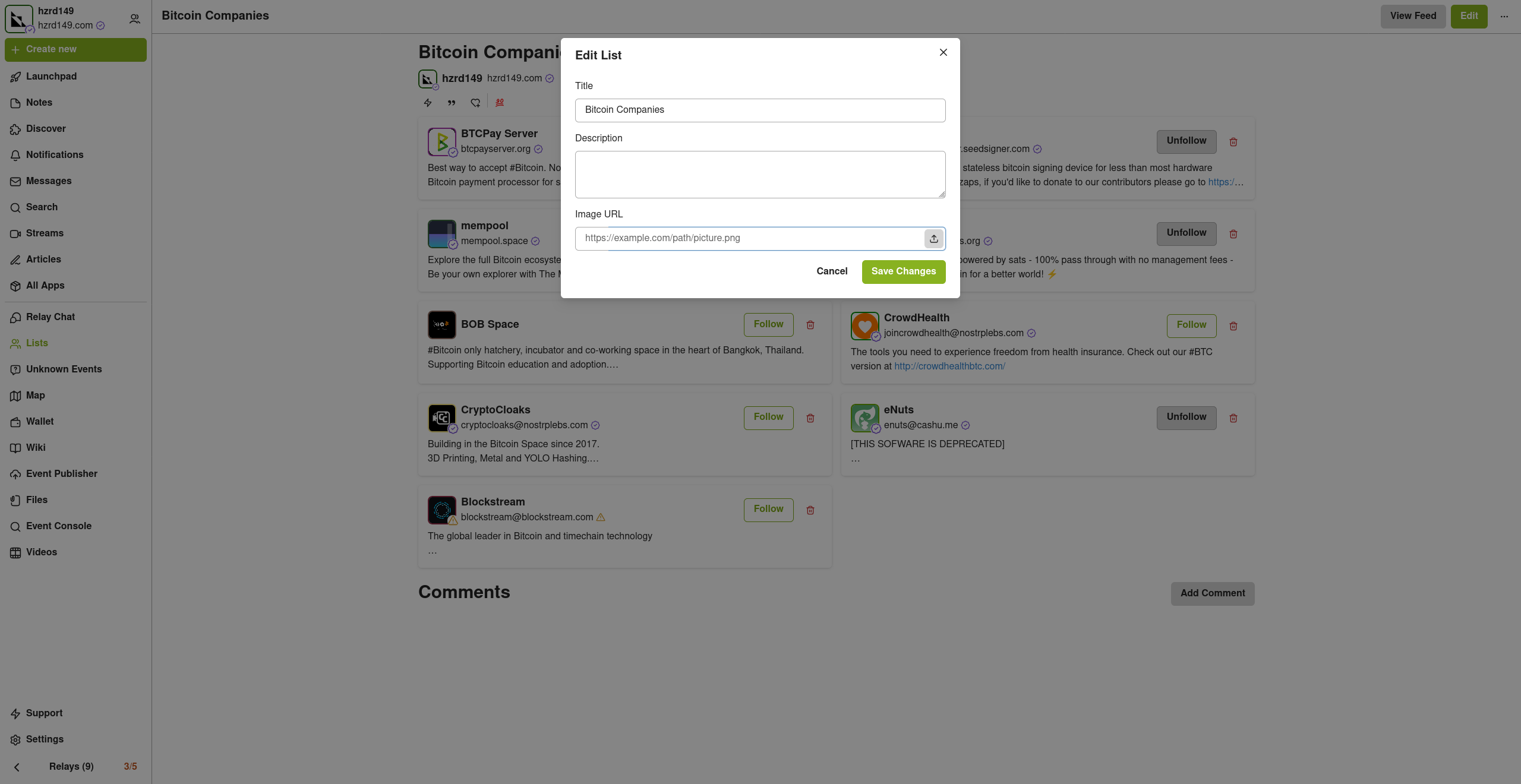
Cleaned up lists
The list views are a little cleaner now, and they have a simple edit modal
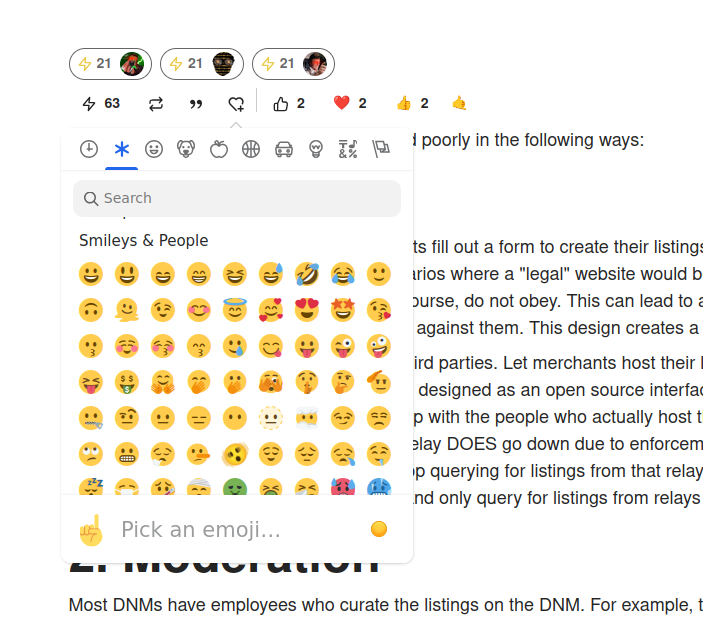
New emoji picker
Just another small improvement that makes the app feel more complete.
Experimental Wallet
There is a new "wallet" view in the app that lets you manage your NIP-60 cashu wallet. its very experimental and probably won't work for you, but its there and I hope to finish it up so the app can support NIP-61 nutzaps.
WARNING: Don't feed the wallet your hard earned sats, it will eat them!
Smaller improvements
- Added NSFW flag for replies
- Updated NIP-48 bunker login to work with new spec
- Linkfy BIPs
- Added 404 page
- Add NIP-22 comments under badges, files, and articles
- Add max height to timeline notes
- Fix articles view freezing on load
- Add option to mirror blobs when sharing notes
- Remove "open in drawer" for notes
-
 @ 6c05c73e:c4356f17
2025-05-10 20:50:06
@ 6c05c73e:c4356f17
2025-05-10 20:50:06Descrição da Embraer (EMBR3)
A Embraer é uma empresa brasileira que nasceu de uma iniciativa do governo brasileiro de implementar uma indústria aeronáutica no país. Após a iniciativa do oficial de aviação do exército, Casimiro Montenegro em convidar o engenheiro Focke-Wulf e seus engenheiros para que atuassem no CTA(Centro Técnico de Aeronáutica). Em, 1953. A empresa surgiu para substituir a importação de jatos para o país.
Mais tarde, sobre a direção de Ozires Silva. Nasce a Embraer SA, em 1969. Em uma sociedade de economia mista vinculada ao ministério da aeronáutica. Mas, em 1992 a empresa foi colocada na lista de empresas a serem privatizadas e em 1994, sob a tutela de Itamar Franco a empresa foi leiloada.
Portanto, os novos majoritários da empresa eram dois fundos de pensão; Previ(20%) e Sistel (20%) e a Cia Bozano, Simonsen(20%) e alguns minoritários tinham algo em torno de (20%) . Vale entender que antes de ser privatizada a empresa estava a passos fortes rumo à falência. E, teve que passar por renovações após se tornar privada.
Contudo, vale lembrar também que alguns anos após a privatização, a empresa passou a figurar como a terceira maior fabricante de jatos comerciais do mundo. E, uma das empresas mais valiosas da Bovespa.

Visão geral
Primordialmente, a Embraer é uma empresa que atua projetando, fabricando e vendendo suas próprias aeronaves. Nesse segmento, ela conta com algumas classes de aviões: Defesa e segurança, comercial e agro. Ademais, estende- se também a serviços e suportes prestados.
A Embraer também atua no desenvolvimento de softwares para a indústria aeronáutica e conta com um dos centros de realidade virtual mais avançados e tecnológicos do mundo.
Desde sua fundação a Embraer já entregou mais de 8.000 aeronaves mundo afora. Ela é a maior fabricante de jatos de até 150 lugares e a maior exportadora de bens de alto valor agregado. Ela detém escritórios, centros de serviços e distribuição na África, Ásia e Europa.

Mercado
Com um mundo cada vez mais rápido e mais globalizado. A frase: "tempo é dinheiro". Nunca antes na história fez mais sentido. A demanda por voos domésticos e internacionais segue cada vez maior e com demanda para muito mais.
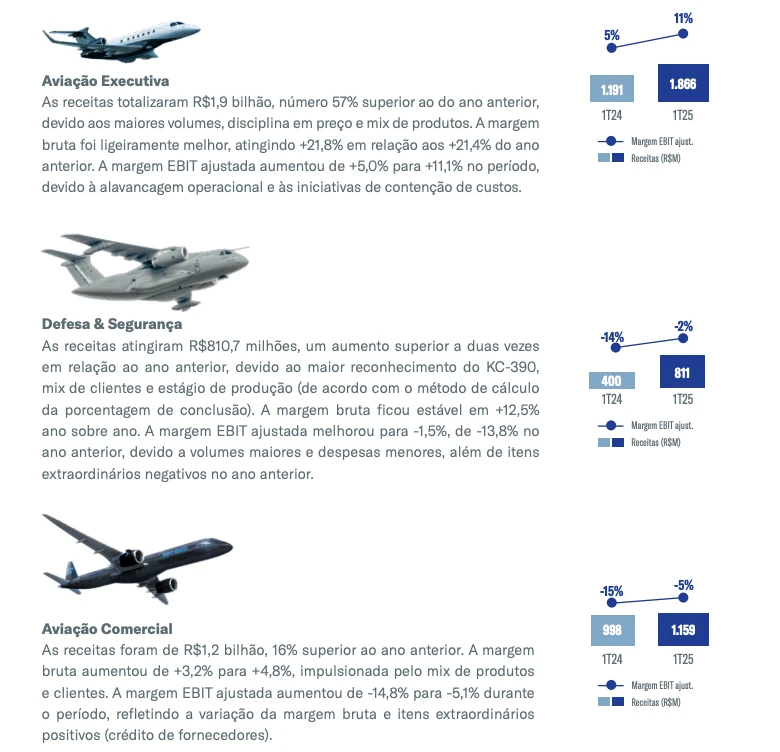
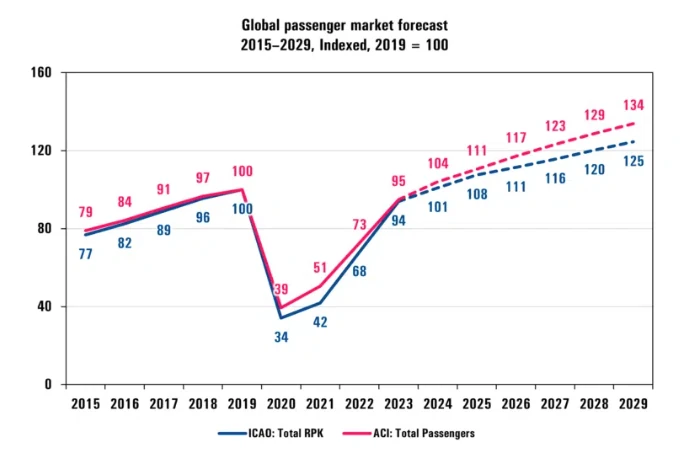
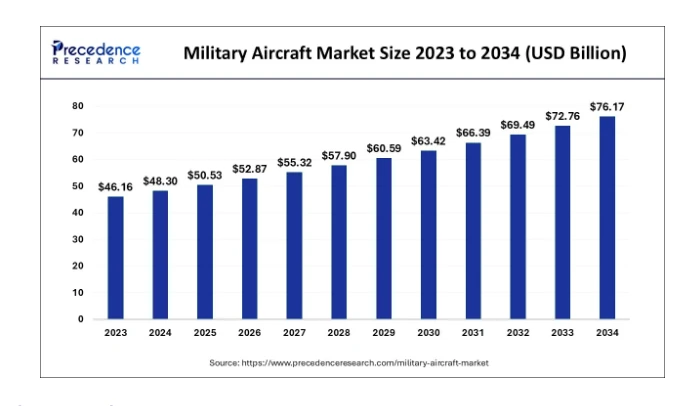
Entretanto, as maiores vendas da empresa não vieram do setor comercial. Mas, sim em defesa e segurança. Com um aumento de 12% (-14% em 1T24 vs -2% 1 T 25) nas vendas por aeronaves de defesa. Esse segmento foi o que mais cresceu nos últimos meses. Em partes pelas tensões geopolíticas e em partes pelo reconhecimento do KC-390.

A demanda por aviões militares só aumenta e segundo pesquisas é um mercado que pode alcançar $29bi até 2034.
Oportunidades
1 - Pedidos aumentaram
Olhando esses cenários. Eu enxergo 3 grandes oportunidades dentro da Embraer. A primeira e mais óbvia é sobre as vendas de aeronaves de defesa e também a parte executiva.
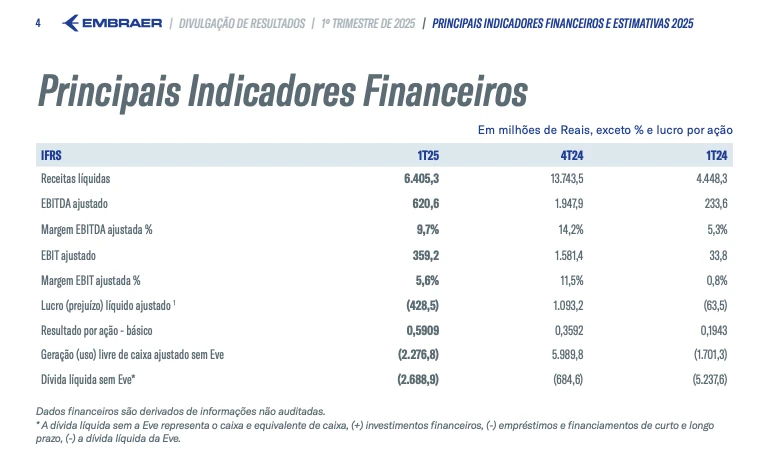
Apesar de ter entregado 30 jatos no 1T25. A empresa reportou que tem pedidos na casa dos $26bi, o que representa um aumento de 25% em relação ao período similar do último ano. Isso é enorme para os acionistas!
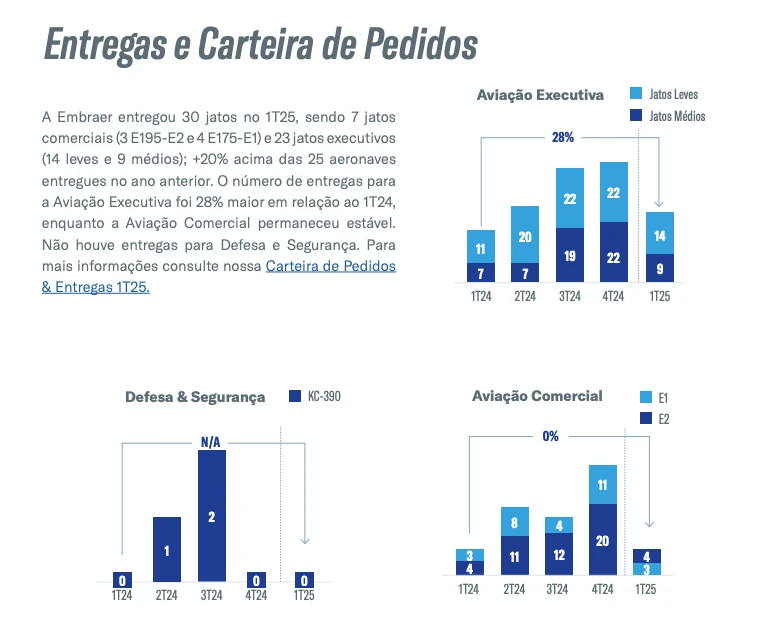
Seguindo a lógica, quanto maiores as vendas de aeronaves. Mais demanda você terá por serviços e suportes. Essa jogada é muito esperta, você vende a solução e detém a ferramenta para manter ela. Apesar da empresa ter reportado prejuízo -R$429mi.
Estou otimista pois a empresa tem uma grande leva de pedidos para entregar, que vai ocasionar o nosso segundo item…
2 - Ativos em caixa
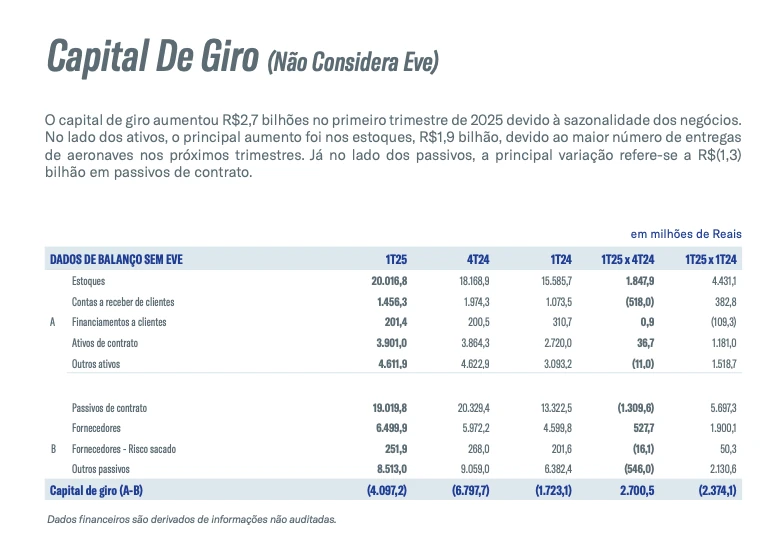
Para contextualizar, a empresa está sentada sobre um capital de giro de R$2.7bi em 1T25. Em função da sazonalidade. Seus ativos aumentaram, em razão de um estoque de R$1,9Bi. Que são respectivos a entrega de aeronaves para os próximos trimestres.
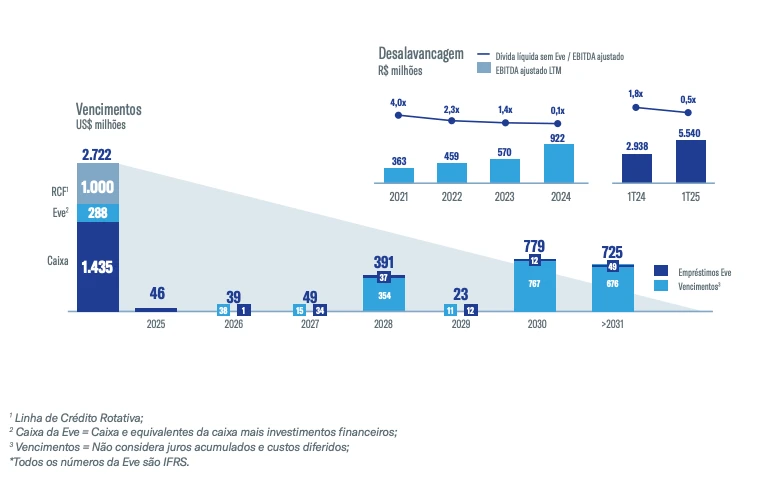
Isso elevou o fluxo de caixa livre para R$2.3bi em 1T2025. Soma se todo esse caixa a redução da dívida que saiu de 1,8 x para 0,5 x no mesmo período. Reduzindo a alavancagem da empresa.
3 - Aviões de defesa e segurança
Aqui é onde está o “pulo do gato”. A demanda por aeronaves desse tipo aumentou muito, como dito anteriormente. E, a Embraer está muito bem posicionada e consolidada como uma marca de prestígio global. Colômbia, clientes Africanos, Áustria e Holanda. São clientes confirmados que já encomendaram para a Embraer.


Riscos
Na minha visão, o maior risco hoje em se investir em Embraer. São as chamadas "golden shares” do governo. Esse é de longe o fator que mais me preocupa. Mesmo, não sendo majoritário. Mas, sabemos como as coisas por aqui funcionam.
Ademais, um risco menor que percebo. É justamente pelas ações estarem no "hype". Isso pode fazer com que o pequeno investidor embarque de cara nessa jornada e veja o preço de suas ações derreterem sistematicamente. Contudo, toda cautela deve ser tomada.

Catalisadores
Vários pontos me chamam a atenção na empresa, tais como:
- O aumento da demanda por aeronaves de defesa e segurança.
- Bom fluxo de vendas para aeronaves executivas.
- O bom fluxo de caixa da empresa.
- A redução de alavancagem.
- A premissa de entrega de várias unidades ao longo dos próximos trimestres.
- E, consequentemente, a variação cambial também pode contribuir e muito para aumentar as margens da empresa.

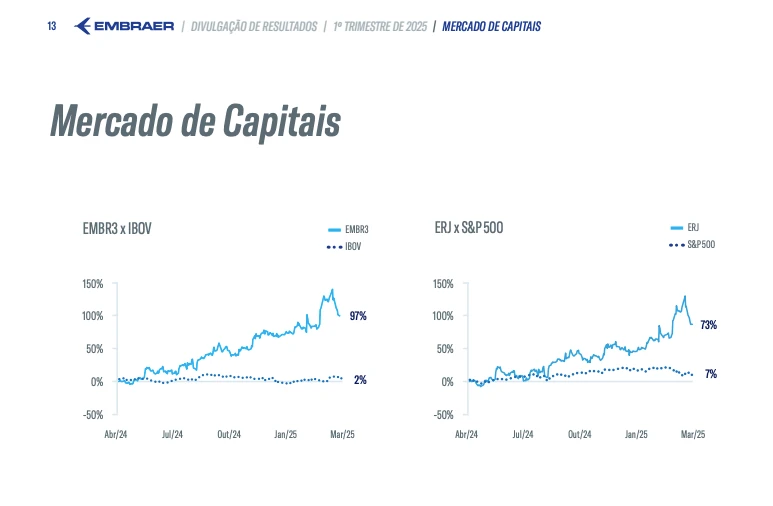
Concluindo quero destacar que a empresa tem muito estoque para entregar (R$1.9BI). Lembre-se, a empresa já vendeu as aeronaves. Por sazonalidade, ela não entregou ainda. E, quando isso ocorrer, vamos ver um volume de dinheiro cada vez maior dentro da empresa. Por isso, não me surpreende que a empresa tenha performado 97% vs 2% do IBOV no mesmo período. Eu olharia com bastante carinho para a empresa nos próximos meses.
FAQ
Quem é o maior acionista da Embraer?
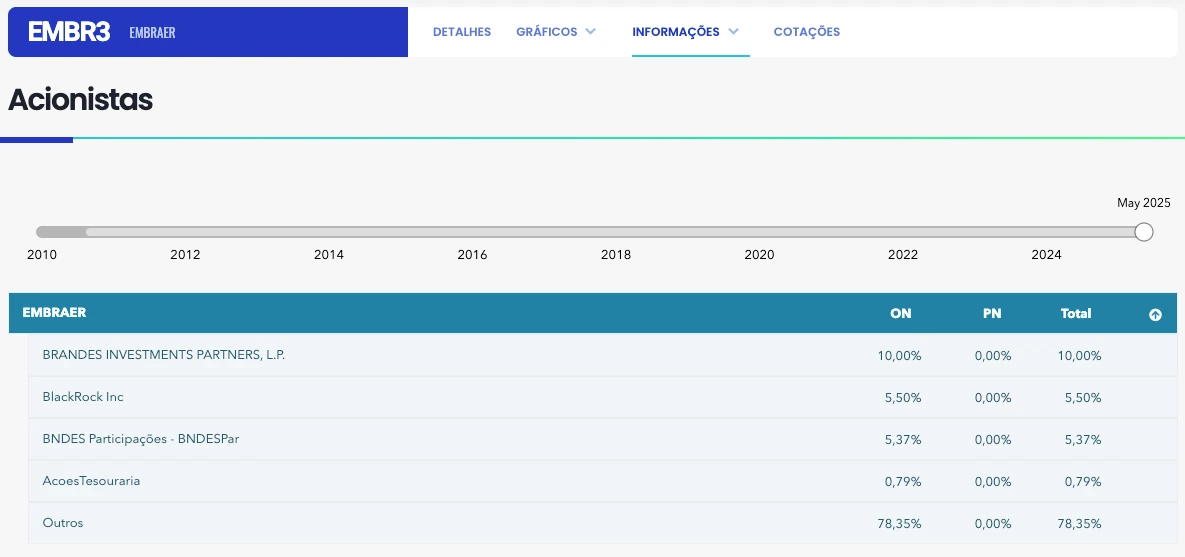
O maior acionista individual da Embraer é a Brandes Investment Partners, LP. A Brandes possui 14,4% das ações da companhia.
Qual a participação do governo na Embraer RI?
O governo, apesar da privatização, detém uma participação acionária especial, conhecida como "golden share", que lhe concede direito de veto em decisões estratégicas da empresa.
Quem é o proprietário da Embraer?
Seus principais acionistas individuais são os fundos estrangeiros Brandes e Mondrian. Qual é o capital social da Embraer RI?
Bio
Investir não precisa ser um bicho de sete cabeças! Na Threedolar, democratizamos o acesso ao mundo dos investimentos, oferecendo conteúdo claro e prático. Comece hoje mesmo a construir seu futuro financeiro!
Disclaimer
Lembre-se: este não é um conselho de investimento. Faça sua própria pesquisa antes de investir. Resultados passados não garantem lucros futuros. Cuide do seu dinheiro!
Referências:
- https://www.fundamentus.com.br/detalhes.php?papel=EMBR3&h=1
- https://pt.wikipedia.org/wiki/Embraer#/media/Ficheiro:EMB-countries.png
- https://pt.wikipedia.org/wiki/Embraer
- https://embraer.com/media/tour/
- https://www.youtube.com/watch?v=pJFnHOYq6h4
- https://www.iata.org/en/pressroom/2025-releases/2025-01-30-01/
- https://www.precedenceresearch.com/military-aircraft-market
- https://www.edrotacultural.com.br/vendas-da-embraer-para-forcas-armadas-registram-alta/
- https://www.poder360.com.br/poder-economia/embraer-anuncia-venda-de-4-aeronaves-para-novo-cliente-africano/
- https://aeroin.net/colombia-deve-comprar-tres-jatos-kc-390-da-embraer-afirma-ministro/#google_vignette
- https://api.mziq.com/mzfilemanager/v2/d/12a56b3a-7b37-4dba-b80a-f3358bf66b71/64eb0439-65bb-2e7f-dd61-ac017ad03886?origin=1 *
-
 @ 57d1a264:69f1fee1
2025-05-08 05:25:48
@ 57d1a264:69f1fee1
2025-05-08 05:25:48Safe Bits & Self Custody Tips
The journey of onboarding a user and create a bitcoin multiSig setup begins far before opening a desktop like Bitcoin Safe (BS) or any other similar application. Bitcoin Safe seems designed for families and people that want to start exploring and learning about multiSig setup. The need for such application and use of it could go much further, defining best practices for private organizations that aim to custody bitcoin in a private and anonymous way, following and enjoy the values and standards bitcoin has been built for.
Intro
Organizations and small private groups like families, family offices and solopreneurs operating on a bitcoin standard will have the need to keep track of transactions and categorize them to keep the books in order. A part of our efforts will be spent ensuring accessibility standards are in place for everyone to use Bitcoin Safe with comfort and safety.
We aim with this project to bring together the three Designathon ideas below: - Bitcoin Safe: improve its overall design and usability. - No User Left Behind: improve Bitcoin Safe accessibility. - Self-custody guidelines for organizations: How Bitcoin Safe can be used by private organization following best self-custody practices.
We are already halfway of the first week, and here below the progress made so far.
Designing an icon Set for Bitcoin Safe
One of the noticeable things when using BS is the inconsistency of the icons, not just in colors and shapes, but also the way are used. The desktop app try to have a clean design that incorporate with all OS (Win, macOS, Linux) and for this reason it's hard to define when a system default icon need to be used or if a custom one can be applied instead. The use of QT Ui framework for python apps help to respond to these questions. It also incorporates and brig up dome default settings that aren't easily overwritten.
Here below you can see the current version of BS:
Defining a more strict color palette for Bitcoin Safe was the first thing!
How much the icons affect accessibility? How they can help users to reach the right functionality? I took the challenge and, with PenPot.app, redesigned the icons based on the grid defined in the https://bitcoinicons.com/ and proposing the implementation of it to have a cleaner and more consistent look'n feel, at least for the icons now.
What's next
I personally look forward to seeing these icons implemented soon in Bitcoin Safe interface. In the meantime, we'll focus on delivering an accessibility audit and evaluate options to see how BS could be used by private organizations aiming to become financially sovereign with self-custody or more complex bitcoin multiSig setups.
One of the greatest innovations BS is bringing to us is the ability to sync the multiSig wallets, including PBST, Categories and labels, through the nostr decentralized protocol, making current key custodial services somehow obsolete. Second-coolest feature that this nostr implementation brings is the ability to have a build-in private chat that connect and enable the various signers of a multiSig to communicate and sign transactions remotely. Where have you seen something like this before?
Categories UX and redesign is also considered in this project. We'll try to understand how to better serve this functionality to you, the user, really soon.
Stay tuned!
originally posted at https://stacker.news/items/974488
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 84da1875:0088fe3c
2025-05-10 04:54:36
@ 84da1875:0088fe3c
2025-05-10 04:54:36O mundo do entretenimento digital está em constante evolução, e o 90PMBET surge como uma das plataformas mais promissoras para quem busca diversão, praticidade e uma experiência envolvente. Com uma interface moderna, ampla variedade de jogos e suporte eficiente, o 90PMBET conquista cada vez mais jogadores brasileiros que desejam explorar novas formas de lazer online com total segurança e acessibilidade.
Conheça a Plataforma 90PMBET A proposta do 90PMBET é simples e objetiva: oferecer um ambiente online completo, onde o usuário pode aproveitar diferentes modalidades de jogos com total comodidade. A plataforma é totalmente otimizada para dispositivos móveis e computadores, garantindo uma navegação fluida e intuitiva em qualquer tela. Desde o primeiro acesso, é possível perceber o cuidado com a experiência do usuário — os menus são bem organizados, as categorias são de fácil acesso e todas as funções principais estão a poucos cliques de distância.
Outro ponto que merece destaque é a segurança. O 90pmbetadota tecnologias avançadas de proteção de dados, como criptografia SSL e autenticação de conta, garantindo que os dados dos usuários estejam protegidos o tempo todo. Além disso, os métodos de pagamento são diversificados e incluem as opções mais populares entre os brasileiros, como PIX, transferência bancária e carteiras digitais.
Variedade de Jogos para Todos os Gostos Um dos maiores atrativos do 90PMBET é a impressionante seleção de jogos disponíveis. A plataforma reúne títulos desenvolvidos pelos principais estúdios do mercado, o que garante qualidade gráfica, boa jogabilidade e mecânicas justas.
Entre os jogos mais populares, destacam-se:
Slots modernos com temáticas variadas, efeitos visuais marcantes e rodadas bônus;
Jogos ao vivo que permitem uma experiência imersiva e interativa com apresentadores reais;
Jogos de mesa tradicionais, como roleta, blackjack e pôquer, em versões otimizadas para o ambiente digital;
Apostas esportivas, com cobertura de eventos nacionais e internacionais em diferentes modalidades, incluindo futebol, basquete e eSports.
Independentemente do estilo de jogo preferido, o 90PMBET oferece opções para todos os perfis de jogadores — desde os mais estratégicos até os que preferem partidas rápidas e dinâmicas.
Uma Experiência do Jogador Realmente Diferenciada A experiência do jogador no 90PMBET é marcada por praticidade, suporte de qualidade e constantes oportunidades de bônus e promoções. A equipe de atendimento está disponível 24 horas por dia, 7 dias por semana, por meio de chat ao vivo e e-mail, sempre pronta para solucionar dúvidas e oferecer suporte técnico.
Outro diferencial é o sistema de recompensas e promoções diárias, que valoriza tanto os novos jogadores quanto os usuários mais antigos. Bônus de boas-vindas, giros gratuitos, cashback e torneios semanais são apenas alguns exemplos das vantagens oferecidas pela plataforma.
Além disso, o 90PMBET promove um ambiente responsável, com ferramentas de controle de tempo de jogo e limites de depósito, ajudando os usuários a manterem uma relação saudável com o entretenimento online.
Conclusão O 90PMBET é mais do que apenas uma plataforma de jogos — é um verdadeiro centro de entretenimento digital pensado para o público brasileiro. Com sua estrutura moderna, ampla variedade de opções, promoções atrativas e foco total na experiência do usuário, o 90PMBET se firma como uma das melhores escolhas para quem busca diversão e emoção no mundo virtual.
Se você ainda não conhece, essa é a hora perfeita para explorar o universo de possibilidades que o 90PMBET tem a oferecer. A diversão está a apenas um clique de distância!
-
 @ 57d1a264:69f1fee1
2025-05-08 05:08:36
@ 57d1a264:69f1fee1
2025-05-08 05:08:36Welcome back to our weekly
JABBB, Just Another Bitcoin Bubble Boom, a comics and meme contest crafted for you, creative stackers!If you'd like to learn more, check our welcome post here.
This week sticker:
Bitcoin SirYou can download the source file directly from the HereComesBitcoin website in SVG and PNG. Use this sticker around SN with the code
The task
Make sure you use this week sticker to design a comic frame or a meme, add a message that perfectly captures the sentiment of the current most hilarious takes on the Bitcoin space. You can contextualize it or not, it's up to you, you chose the message, the context and anything else that will help you submit your comic art masterpiece.
Are you a meme creator? There's space for you too: select the most similar shot from the gifts hosted on the Gif Station section and craft your best meme... Let's Jabbb!
If you enjoy designing and memeing, feel free to check out the JABBB archive and create more to spread Bitcoin awareness to the moon.
Submit each proposal on the relative thread, bounties will be distributed when enough participants submit options.
PS: you can now use HereComesBitcoin stickers to use on Stacker.News
₿e creative, have fun! :D
originally posted at https://stacker.news/items/974483
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ 90c656ff:9383fd4e
2025-05-10 08:02:51
@ 90c656ff:9383fd4e
2025-05-10 08:02:51Bitcoin was conceived as a decentralized system where anyone can participate in the network, validate transactions, and help secure the system. However, over the years, Bitcoin mining has become increasingly concentrated in certain regions of the world, raising concerns about its decentralization and security. This debate has sparked a range of opinions, with some arguing that mining centralization could compromise Bitcoin's fundamental principles.
- Why has mining become centralized in some countries?
Bitcoin mining requires a significant amount of energy and specialized equipment, known as ASICs. Due to factors like electricity costs, climate, and regulation, some regions have become mining hubs, attracting large-scale operations. The main reasons for this concentration include:
01 - Electricity cost: Countries with cheap electricity, such as China (before the ban), Kazakhstan, and some regions of the United States, became mining centers because operational costs are significantly lower.
02 - Favorable climate: Locations with colder temperatures reduce the need for cooling systems for mining equipment, making operations more efficient.
03 - Regulation and tax incentives: Some countries foster favorable environments for mining by offering tax benefits or energy sector incentives.
- Impacts of mining centralization
The centralization of mining in certain countries raises concerns about control over the Bitcoin network. Key risks include:
01 - Censorship risk: If a country with a high concentration of miners decides to regulate or restrict mining, it could temporarily affect the network, making it more vulnerable to attacks or censorship.
02 - 51% attack: One of the biggest concerns is the possibility of a group of miners controlling more than 50% of the network’s hash power, which could allow transaction manipulation. While unlikely, this scenario is a persistent worry in the Bitcoin community.
03 - Reliance on centralized infrastructure: If mining is concentrated in a few regions, failures in local infrastructure—such as power outages or natural disasters—can significantly impact the network.
- Measures to decentralize mining
Despite the trend toward centralization, the Bitcoin network remains resilient, and there are initiatives to make mining more distributed. Some solutions include:
01 - Home and community mining: Encouraging small-scale mining can help distribute hash power more evenly.
02 - Use of renewable energy in diverse regions: As more miners adopt renewable sources, new locations are emerging as decentralized mining centers.
03 - Miner exodus: After China’s mining ban in 2021, many operations relocated to countries like the United States, Canada, and nations in Latin America, helping diversify the network.
In summary, the centralization of mining in certain regions poses a challenge for Bitcoin but does not mean the network is in immediate danger. As the industry evolves, mining is expected to become increasingly distributed, helping to safeguard the network’s security and decentralization. While it's crucial to keep an eye on this issue, Bitcoin continues to prove its resilience, constantly adapting to changes in the mining landscape.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 84da1875:0088fe3c
2025-05-10 04:53:59
@ 84da1875:0088fe3c
2025-05-10 04:53:59No cenário atual do entretenimento digital, a plataforma CC999 vem se destacando como uma das mais inovadoras e completas opções para quem busca emoção, segurança e variedade em um só lugar. Com uma proposta moderna e acessível, o site oferece uma experiência diferenciada, reunindo jogos envolventes, atendimento de qualidade e uma navegação simples e rápida, ideal tanto para iniciantes quanto para jogadores mais experientes.
Conheça a Plataforma CC999 Desde o primeiro acesso, é fácil perceber que a CC999 foi desenvolvida com foco no usuário. Seu layout é intuitivo, com menus organizados e compatibilidade total com dispositivos móveis, permitindo que você aproveite tudo o que a plataforma oferece diretamente do seu celular, tablet ou computador.
Além disso, o processo de cadastro é rápido e descomplicado. Em poucos minutos, você já pode criar sua conta e começar a explorar os recursos disponíveis. Outro diferencial é o compromisso com a segurança dos dados, utilizando criptografia de ponta e sistemas confiáveis de autenticação para garantir a tranquilidade de todos os usuários.
Jogos para Todos os Gostos A variedade de jogos disponíveis no CC999 é um dos grandes atrativos da plataforma. Ela conta com uma seleção que vai desde jogos clássicos e tradicionais até opções modernas com gráficos impressionantes e mecânicas envolventes. Alguns dos destaques incluem:
Roleta Virtual: Ideal para quem gosta de adrenalina e sorte, com várias versões disponíveis.
Slots Online: Máquinas de giro com temas variados, efeitos visuais marcantes e grandes chances de ganho.
Cartas e Estratégia: Jogos como pôquer e blackjack oferecem experiências desafiadoras para quem curte usar o raciocínio lógico.
Títulos Ao Vivo: Com interação em tempo real, esses jogos garantem uma imersão total e realista, aproximando o jogador da atmosfera presencial.
A CC999 trabalha com provedores renomados, garantindo qualidade, fluidez e jogabilidade de alto nível em todos os títulos. Isso significa que, além da diversão, o jogador tem acesso a conteúdos justos e auditados.
Experiência do Jogador: Conectividade e Recompensas A experiência dos usuários na plataforma é constantemente aprimorada com base em feedbacks e atualizações tecnológicas. O atendimento ao cliente está disponível 24 horas por dia, todos os dias da semana, pronto para resolver qualquer dúvida ou problema com agilidade e cordialidade.
Outro ponto que merece destaque são as promoções e bônus oferecidos pela CC999. Desde o primeiro depósito até campanhas sazonais, os jogadores têm acesso a recompensas atrativas, o que torna a jornada ainda mais interessante. O sistema de fidelidade também premia a constância dos usuários, oferecendo vantagens exclusivas para membros frequentes.
Conclusão A CC999 chega como uma excelente alternativa para quem busca entretenimento online de qualidade. Com uma interface moderna, jogos variados, suporte eficiente e promoções constantes, a plataforma conquista pela seriedade e compromisso com a diversão do usuário. Seja você um veterano ou alguém começando agora nesse universo, o CC999 tem tudo o que você precisa para se divertir com segurança e emoção.
-
 @ 6c05c73e:c4356f17
2025-05-10 20:46:26
@ 6c05c73e:c4356f17
2025-05-10 20:46:26Porque investir R$100
Um guia politicamente diferente de investimento
Você já certamente se pegou na seguinte situação. Paguei tudo o que devia. E, agora me sobrou cem reais para investir.
Principalmente, se você é novo e está no seu primeiro emprego. Isso é muito comum. Contudo, mesmo os mais experimentados passam por isso.
No entanto, vem aquela pergunta na cabeça. Será que eu realmente preciso investir esses cem reais? Afinal, é uma quantia pequena e qual seria o retorno disso?
Contudo, para responder sua dúvida. A resposta é sempre sim. Se, algum dia na sua vida. Você quiser acumular recursos e escapar desse círculo vicioso. Precisa acumular e investir.
Todavia, vamos analisar nesse artigo alguns outros aspectos que podem elevar x10 esse valor investido.
Quando investir R$100?
Agora, amanhã ou ano que vem?
Muitos pensam que todo dinheiro ganho precisa IMEDIATAMENTE ser investido. E, na verdade isso não precisa ser assim.
Portanto, todo o dinheiro ganho deve ser aplicado com diligência. Decidir quando investir o dinheiro é uma tarefa crucial. Mas, antes disso acontecer. Você precisa definir seus objetivos.
Sobretudo, aonde você vai colocar seu dinheiro. Vai determinar o ritmo como investe. E, isso é crucial em uma jornada de investimentos.
Aonde?
“Para manter uma fogueira, tem que botar mais lenha”
Espera um pouco. O que essa frase quer dizer? Vamos criar uma situação hipotética aqui e analisar três formas de investimento:
Investir em ações na bolsa de valores (renda variável) Investir em si mesmo (aumentar capacidade)
Primeira hipótese:
Você investiu R$100 o ano todo. Todos os meses. Isso gerou um bruto de R$1.200. Você estudo e se dedicou. Analisou ações, assistiu a vários vídeos e análises. E fez 15% de retorno no ano.
Nessa primeira hipótese, você acumulou R$1.200 + 15% de retorno (R$180). O que te rendeu R$1380 brutos. Com essa quantia a incidência de impostos não existe. Então, sem DARFS por aqui.
Compensou investir 2 horas por dia * 200 dias no ano =1.752.000 min. Para poder ganhar R$180?
Dahhhh, não. Você ficou mais experiente e aprendeu. Mas, a quantia é muito pequena e não faz cócegas. Tampouco te faz sorrir. E te tira dessa situação.
Segunda hipótese:
Eu não sei qual o seu ofício nesse momento. Mas, eu sei de duas coisas. Ou você gosta e quer se especializar. Ou você quer trocar de ofício logo logo. Então, meu consagrado(a). Você já sabe…
Agora, vamos pegar esses R$100 mensais e investir em um curso técnico. Pois, é mais rápido que uma faculdade. Será seu primeiro diploma oficial, te torna alguém e te dá um ofício.
Assim sendo, você tem grandes chances de trocar de trabalho. Ter aumento salarial é certamente no prazo de um ano. Você vai ganhar muitos mais que os R$180 brutos de rentabilidade do primeiro caso.
Agora, quer saber a real porque ninguém te fala isso no YouTube, Instagram e TikTok?
Meu consagrado, as pessoas só te recomendam o que é bom para elas. Não há nada de errado com isso. O que quero te fazer enxergar aqui. É que você está sozinho (ou tem que estar, para refletir) e precisa escolher o que é melhor para você.
Contudo, é importante para para pensar por um tempo e entender o que vai ser melhor para você. Qual melhor caminho seguir. E ponto, só você sabe o que é melhor para você.
Como?
Para fechar nosso raciocínio de hoje. Vamos a pergunta de um milhão de dólares. Mas, como eu faço isso? Meu querido(a), você vai fazer um exercício comigo logo menos.
Você vai deixar seu celular no silencioso. Colocar um timer de 15 minutos. Pegar um papel e caneta e anotar em uma folha o que você gosta + o que você você gostaria de fazer da sua vida.
Logo, essa lista tem que conter o SEU gosto. Não do seu amigo, do influenciador, da celebridade ou do atleta. Essas pessoas tem influência sobre sua vida? Claro! Mas, cabe a você refletir sobre o que realmente quer.
Naturalmente, você não vai colocar lá na sua lista; quero uma Ferrari esse ano. Porque não é assim que funciona. Na real, você pode querer a Ferrari. Sem problema algum.
Mas, saiba que antes da Ferrari. Vai ter que vir o Gol, o Civic, a 325, o 911 e daí a Ferrari. Tudo na vida é passo meu caro(a). Ou você acha que vai dar saltos quânticos na vida sem estar preparado? Não é assim que a vida funciona.
Em suma,
para concluir esse texto. Vamos fazer o resumão prático do que fazer com cem reais mensais:
*** Tire um tempo para entender o que quer e o que tu gosta. * Visualize e anote seus objetivos que quer em uma folha. * Invista em você incansavelmente. * Você vai chegar ao topo da montanha. Mas, tem que subir um nível por vez.**
Bio
Se chegou até aqui é porque gostou e quer mudar de vida. Manda pro teu colega que tá precisando desse tapa de luva. Obrigado pelo seu tempo.
-
 @ 088436cd:9d2646cc
2025-05-01 21:01:55
@ 088436cd:9d2646cc
2025-05-01 21:01:55The arrival of the coronavirus brought not only illness and death but also fear and panic. In such an environment of uncertainty, people have naturally stocked up on necessities, not knowing when things will return to normal.
Retail shelves have been cleared out, and even online suppliers like Amazon and Walmart are out of stock for some items. Independent sellers on these e-commerce platforms have had to fill the gap. With the huge increase in demand, they have found that their inventory has skyrocketed in value.
Many in need of these items (e.g. toilet paper, hand sanitizer and masks) balk at the new prices. They feel they are being taken advantage of in a time of need and call for intervention by the government to lower prices. The government has heeded that call, labeling the independent sellers as "price gougers" and threatening sanctions if they don't lower their prices. Amazon has suspended seller accounts and law enforcement at all levels have threatened to prosecute. Prices have dropped as a result and at first glance this seems like a victory for fair play. But, we will have to dig deeper to understand the unseen consequences of this intervention.
We must look at the economics of the situation, how supply and demand result in a price and how that price acts as a signal that goes out to everyone, informing them of underlying conditions in the economy and helping coordinate their actions.
It all started with a rise in demand. Given a fixed supply (e.g., the limited stock on shelves and in warehouses), an increase in demand inevitably leads to higher prices. Most people are familiar with this phenomenon, such as paying more for airline tickets during holidays or surge pricing for rides.
Higher prices discourage less critical uses of scarce resources. For example, you might not pay $1,000 for a plane ticket to visit your aunt if you can get one for $100 the following week, but someone else might pay that price to visit a dying relative. They value that plane seat more than you.
*** During the crisis, demand surged and their shelves emptied even though
However, retail outlets have not raised prices. They have kept them low, so the low-value uses of things like toilet paper, masks and hand sanitizer has continued. Often, this "use" just takes the form of hoarding. At everyday low prices, it makes sense to buy hundreds of rolls and bottles. You know you will use them eventually, so why not stock up? And, with all those extra supplies in the closet and basement, you don't need to change your behavior much. You don't have to ration your use.
At the low prices, these scarce resources got bought up faster and faster until there was simply none left. The reality of the situation became painfully clear to those who didn't panic and got to the store late: You have no toilet paper and you're not going to any time soon.
However, if prices had been allowed to rise, a number of effects would have taken place that would have coordinated the behavior of everyone so that valuable resources would not have been wasted or hoarded, and everyone could have had access to what they needed.
On the demand side, if prices had been allowed to rise, people would have begun to self-ration. You might leave those extra plies on the roll next time if you know they will cost ten times as much to replace. Or, you might choose to clean up a spill with a rag rather than disposable tissue. Most importantly, you won't hoard as much. That 50th bottle of hand sanitizer might just not be worth it at the new, high price. You'll leave it on the shelf for someone else who may have none.
On the supply side, higher prices would have incentivized people to offer up more of their stockpiles for sale. If you have a pallet full of toilet paper in your basement and all of the sudden they are worth $15 per roll, you might just list a few online. But, if it is illegal to do so, you probably won't.
Imagine you run a business installing insulation and have a few thousand respirator masks on hand for your employees. During a pandemic, it is much more important that people breathe filtered air than that insulation get installed, and that fact is reflected in higher prices. You will sell your extra masks at the higher price rather than store them for future insulation jobs, and the scarce resource will be put to its most important use.
Producers of hand sanitizer would go into overdrive if prices were allowed to rise. They would pay their employees overtime, hire new ones, and pay a premium for their supplies, making sure their raw materials don't go to less important uses.
These kinds of coordinated actions all across the economy would be impossible without real prices to guide them. How do you know if it makes sense to spend an extra $10k bringing a thousand masks to market unless you know you can get more than $10 per mask? If the price is kept artificially low, you simply can't do it. The money just isn't there.
These are the immediate effects of a price change, but incredibly, price changes also coordinate people's actions across space and time.
Across space, there are different supply and demand conditions in different places, and thus prices are not uniform. We know some places are real "hot spots" for the virus, while others are mostly unaffected. High demand in the hot spots leads to higher prices there, which attracts more of the resource to those areas. Boxes and boxes of essential items would pour in where they are needed most from where they are needed least, but only if prices were allowed to adjust freely.
This would be accomplished by individuals and businesses buying low in the unaffected areas, selling high in the hot spots and subtracting their labor and transportation costs from the difference. Producers of new supply would know exactly where it is most needed and ship to the high-demand, high-price areas first. The effect of these actions is to increase prices in the low demand areas and reduce them in the high demand areas. People in the low demand areas will start to self-ration more, reflecting the reality of their neighbors, and people in the hotspots will get some relief.
However, by artificially suppressing prices in the hot spot, people there will simply buy up the available supply and run out, and it will be cost prohibitive to bring in new supply from low-demand areas.
Prices coordinate economic actions across time as well. Just as entrepreneurs and businesses can profit by transporting scarce necessities from low-demand to high-demand areas, they can also profit by buying in low-demand times and storing their merchandise for when it is needed most.
Just as allowing prices to freely adjust in one area relative to another will send all the right signals for the optimal use of a scarce resource, allowing prices to freely adjust over time will do the same.
When an entrepreneur buys up resources during low-demand times in anticipation of a crisis, she restricts supply ahead of the crisis, which leads to a price increase. She effectively bids up the price. The change in price affects consumers and producers in all the ways mentioned above. Consumers self-ration more, and producers bring more of the resource to market.
Our entrepreneur has done a truly incredible thing. She has predicted the future, and by so doing has caused every individual in the economy to prepare for a shortage they don't even know is coming! And, by discouraging consumption and encouraging production ahead of time, she blunts the impact the crisis will have. There will be more of the resource to go around when it is needed most.
On top of this, our entrepreneur still has her stockpile she saved back when everyone else was blithely using it up. She can now further mitigate the damage of the crisis by selling her stock during the worst of it, when people are most desperate for relief. She will know when this is because the price will tell her, but only if it is allowed to adjust freely. When the price is at its highest is when people need the resource the most, and those willing to pay will not waste it or hoard it. They will put it to its highest valued use.
The economy is like a big bus we are all riding in, going down a road with many twists and turns. Just as it is difficult to see into the future, it is difficult to see out the bus windows at the road ahead.
On the dashboard, we don't have a speedometer or fuel gauge. Instead we have all the prices for everything in the economy. Prices are what tell us the condition of the bus and the road. They tell us everything. Without them, we are blind.
Good times are a smooth road. Consumer prices and interest rates are low, investment returns are steady. We hit the gas and go fast. But, the road is not always straight and smooth. Sometimes there are sharp turns and rough patches. Successful entrepreneurs are the ones who can see what is coming better than everyone else. They are our navigators.
When they buy up scarce resources ahead of a crisis, they are hitting the brakes and slowing us down. When they divert resources from one area to another, they are steering us onto a smoother path. By their actions in the market, they adjust the prices on our dashboard to reflect the conditions of the road ahead, so we can prepare for, navigate and get through the inevitable difficulties we will face.
Interfering with the dashboard by imposing price floors or price caps doesn't change the conditions of the road (the number of toilet paper rolls in existence hasn't changed). All it does is distort our perception of those conditions. We think the road is still smooth--our heavy foot stomping the gas--as we crash onto a rocky dirt road at 80 miles per hour (empty shelves at the store for weeks on end).
Supply, demand and prices are laws of nature. All of this is just how things work. It isn't right or wrong in a moral sense. Price caps lead to waste, shortages and hoarding as surely as water flows downhill. The opposite--allowing prices to adjust freely--leads to conservation of scarce resources and their being put to their highest valued use. And yes, it leads to profits for the entrepreneurs who were able to correctly predict future conditions, and losses for those who weren't.
Is it fair that they should collect these profits? On the one hand, anyone could have stocked up on toilet paper, hand sanitizer and face masks at any time before the crisis, so we all had a fair chance to get the supplies cheaply. On the other hand, it just feels wrong that some should profit so much at a time when there is so much need.
Our instinct in the moment is to see the entrepreneur as a villain, greedy "price gouger". But we don't see the long chain of economic consequences the led to the situation we feel is unfair.
If it weren't for anti-price-gouging laws, the major retailers would have raised their prices long before the crisis became acute. When they saw demand outstrip supply, they would have raised prices, not by 100 fold, but gradually and long before anyone knew how serious things would have become. Late comers would have had to pay more, but at least there would be something left on the shelf.
As an entrepreneur, why take risks trying to anticipate the future if you can't reap the reward when you are right? Instead of letting instead of letting entrepreneurs--our navigators--guide us, we are punishing and vilifying them, trying to force prices to reflect a reality that simply doesn't exist.
In a crisis, more than any other time, prices must be allowed to fluctuate. To do otherwise is to blind ourselves at a time when danger and uncertainty abound. It is economic suicide.
In a crisis, there is great need, and the way to meet that need is not by pretending it's not there, by forcing prices to reflect a world where there isn't need. They way to meet the need is the same it has always been, through charity.
If the people in government want to help, the best way for the to do so is to be charitable and reduce their taxes and fees as much as possible, ideally to zero in a time of crisis. Amazon, for example, could instantly reduce the price of all crisis related necessities by 20% if they waived their fee. This would allow for more uses by more people of these scarce supplies as hoarders release their stockpiles on to the market, knowing they can get 20% more for their stock. Governments could reduce or eliminate their tax burden on high-demand, crisis-related items and all the factors that go into their production, with the same effect: a reduction in prices and expansion of supply. All of us, including the successful entrepreneurs and the wealthy for whom high prices are not a great burden, could donate to relief efforts.
These ideas are not new or untested. This is core micro economics. It has been taught for hundreds of years in universities the world over. The fact that every crisis that comes along stirs up ire against entrepreneurs indicates not that the economics is wrong, but that we have a strong visceral reaction against what we perceive to be unfairness. This is as it should be. Unfairness is wrong and the anger it stirs in us should compel us to right the wrong. Our anger itself isn't wrong, it's just misplaced.
Entrepreneurs didn't cause the prices to rise. Our reaction to a virus did that. We saw a serious threat and an uncertain future and followed our natural impulse to hoard. Because prices at major retail suppliers didn't rise, that impulse ran rampant and we cleared the shelves until there was nothing left. We ran the bus right off the road and them blamed the entrepreneurs for showing us the reality of our situation, for shaking us out of the fantasy of low prices.
All of this is not to say that entrepreneurs are high-minded public servants. They are just doing their job. Staking your money on an uncertain future is a risky business. There are big risks and big rewards. Most entrepreneurs just scrape by or lose their capital in failed ventures.
However, the ones that get it right must be allowed to keep their profits, or else no one will try and we'll all be driving blind. We need our navigators. It doesn't even matter if they know all the positive effects they are having on the rest of us and the economy as a whole. So long as they are buying low and selling high--so long as they are doing their job--they will be guiding the rest of us through the good times and the bad, down the open road and through the rough spots.
-
 @ 57d1a264:69f1fee1
2025-05-07 06:56:25
@ 57d1a264:69f1fee1
2025-05-07 06:56:25Wild parrots tend to fly in flocks, but when kept as single pets, they may become lonely and bored https://www.youtube.com/watch?v=OHcAOlamgDc
Source: https://www.smithsonianmag.com/smart-news/scientists-taught-pet-parrots-to-video-call-each-other-and-the-birds-loved-it-180982041/
originally posted at https://stacker.news/items/973639
-
 @ 95543309:196c540e
2025-05-10 07:29:13
@ 95543309:196c540e
2025-05-10 07:29:13:bob:
rant
why the fuck bunkers and stuff try to enctypt long text articles with nip 44
end rant
-
 @ 3c7dc2c5:805642a8
2025-05-10 19:15:50
@ 3c7dc2c5:805642a8
2025-05-10 19:15:50🧠Quote(s) of the week:
'Bitcoin is a high-IQ, low-time-preference asset in a world addicted to DoorDash, dopamine, and debt. Holding Bitcoin requires patience, conviction, and the ability to not panic when CNBC tells you it’s dead for the 47th time. That rules out, oh, I don’t know - 95% of the population? This isn’t some egalitarian revolution. This is a cognitive filter disguised as a monetary network. The rich, the strategic, the elite - those who understand volatility as an opportunity - will stack the hardest asset on Earth while the masses beg for interest rate cuts and $600 stimmies to buy groceries they can't afford.
It's not a level playing field. It's a time-preference war, and Bitcoin is the scoreboard. And every cycle, we watch it happen again. The media ridicules it, the politicians fear it, and the smart money buys more. While fiat punishes savers and rewards financial nihilism, Bitcoin inverts the whole structure. It’s a vault for those who can delay gratification, think generationally, and understand that true wealth is preserved rather than printed. The game isn’t rigged. It’s just calibrated for adults.' - Adam Livingston
'Bitcoin is an extremely simple thesis. If you think governments will stop debasing and debanking: number go down. If you think they won’t stop debasing and debanking: number go up'- Alex Gladstein
Something to ponder on.
🧡Bitcoin news🧡
On the 28th of April:
➡️Hunter Horsley: 'Bitcoin at $94k, yet — Google searches for "Bitcoin" near long-term lows. This hasn't been retail-driven. Institutions, advisors, corporations, and nations have come into the space. The types of investors buying Bitcoin are expanding.'
➡️Daniel Batten: 'Cambridge has just released their updated report on Bitcoin mining. For the first time, their report shows that most (52.4%) of the Bitcoin network is now powered by zero-emission energy sources (up from 37% in their last report).
Here's a summary of their findings:
https://x.com/DSBatten/status/1916903476610650202
You can read the full report here
➡️Arizona’s Bitcoin Reserve bill (SB 1025) just passed the House and now heads to the desk of Governor Katie Hobbs. However, Governor Hobbs has vowed to veto any legislation until a budget impasse over funding for disability services is resolved.
On the 29th of April:
➡️Bitcoin Archive: 'South Korea's ruling party to approve spot Bitcoin ETFs, scrap restrictive banking crypto rules, and introduce crypto-friendly framework THIS YEAR, if it wins the June election.'
➡️President Trump's Executive Director says there is a "space race" amongst countries to accumulate Bitcoin: "We view Bitcoin as digital gold."
➡️U.S. to "turbo-charge" Bitcoin mining growth by allowing Bitcoin miners to build power plants and data centres near natural gas fields - Howard Lutnick, Commerce Secretary
➡️Japanese clothing company ANAP Holdings Inc. bought 35 Bitcoins worth $3.3 million. ANAP now holds 51.7 BTC, joining Japan’s growing corporate Bitcoin treasury movement.
➡️Semler Scientific adds 165 BTC for $15.7M, bringing total holdings to 3,467 BTC. The company reports a 23.8% BTC yield year-to-date.
➡️The Bitcoin hashrate has already surged over 17% since the start of the year.
➡️'This shattered a major myth for me: gold production isn’t slowing down—it’s accelerating. According to NYDIG, annual gold mining has been steadily increasing over time, about 1.6% per year, thanks to better extraction technology. In fact, 2024 saw a 1% year-over-year increase, setting an all-time high in gold output (World Gold Council). So why do so many still believe the outdated narrative that gold is becoming harder to find? The truth is: gold is effectively unlimited in supply—we just get better at digging it up. If that surprises you, you're probably not nearly bullish enough on Bitcoin.' - Robert Hefner https://i.ibb.co/JWCHndQk/Gpu-W9-R1-Xw-AAiy-Cv.jpg
On the 30th of April:
➡️The Bank of Italy identifies Bitcoin as an emerging risk factor with concerns for the financial system.
"The strong growth of Bitcoin and other crypto-assets with high price volatility means risks not only for investors but also potentially for financial stability, given the growing interconnections between the digital asset ecosystem, the traditional financial sector, and the real economy,”
Tell me you are scared of Bitcoin without telling me you are scared of Bitcoin.
➡️4 major wirehouses managing $10 TRILLION to start offering Bitcoin ETFs to clients this year, says BitWise CIO Matt Hougan. Merrill Lynch, Morgan Stanley, Wells Fargo, and UBS are coming to the party.
➡️Roswell, New Mexico, becomes the 1st United States city to launch a strategic Bitcoin reserve.
➡️BlackRock’s Bitcoin ETF IBIT has hit 600,000 BTC!
➡️Semler Scientific bought 165 Bitcoins worth $15.7m. They now hold 3,467 BTC on their balance sheet.
➡️Bitcoin News: 'El Salvador is still buying Bitcoin despite an IMF loan deal that required it to stop. Economy Minister Maria Luisa Hayem confirmed ongoing accumulation, calling Bitcoin “an important project” and a key asset for both the government and private sector.'
➡️New whales are buying Bitcoin faster than ever before!
➡️'ZachXBT says the $330M Bitcoin theft involved an elderly U.S. victim targeted by social engineering. The stolen 3,520 BTC were laundered through six exchanges and swapped into Monero, triggering a 50% price spike due to thin liquidity.' -Bitcoin News
On the 1st of May:
➡️North Carolina Bitcoin Reserve Bill has passed the House! This bill enables state retirement funds to invest up to $ 13 B.
➡️Tether’s latest attestation states the company holds $7.6 billion in Bitcoin.
➡️Europe's largest Bitcoin treasury company, The Blockchain Group, aspires to hold 1% of the total Bitcoin supply by 2033.
➡️FiatHawk: 'Central banks create fake money to buy real gold, and we’re supposed to pretend this isn’t theft. The game is rigged. Their paper is trash. Gold knows it. Bitcoin ends it. Stop believing the lie.
https://i.ibb.co/mrBZtY5P/Gpl4kl-ak-AA-xv-D.png
When the debt bubble collapses, only sound money with zero counterparty risk matters. Currently, sound money is less than 5% of debt money, and Bitcoin is so tiny it is barely visible on the chart. Stay humble and keep stacking.' https://i.ibb.co/QF0Vf9k8/Gpu-CCIWa-YAAng1-U.png
On the 2nd of May:
➡️ Regarding the whole OP_Return debate.
Grok: ++Key Points: ++ * The OP_RETURN debate in Bitcoin centers on whether its blockchain should store data beyond financial transactions, with ongoing controversy. * It began in 2010 with concerns about blockchain bloat, intensified in 2014 with the "OP_Return Wars," and continues today. * Research suggests the debate reflects a balance between Bitcoin's monetary purpose and potential for broader applications like Dapps. * Compromises, like setting a 40-byte limit in 2014, aimed to address concerns but didn't fully resolve tensions, influencing platforms like Ethereum.
++Background++ OP_RETURN is a Bitcoin script opcode allowing small data storage in transactions, useful for timestamping or Dapps, but raising concerns about blockchain bloat.
++Historical Context++
The debate started in 2010 with the BitDNS proposal, where Satoshi Nakamoto worried about scalability, leading to Namecoin. It peaked in 2014 with Counterparty's use, leading to a 40-byte limit compromise, later adjusted to 83 bytes by 2016.
++Recent Developments++ By 2018-2019, high OP_RETURN usage (20% of transactions) sparked fee debates, but usage has since declined, though data remains, with recent 2023 controversies over size limits.
If you are interested in Bitcoin, then you should check out the following video.
Great video from @GrassFedBitcoin explaining the current OP_RETURN situation. The choice isn’t between bloating the UTXO set or increasing OP_RETURN, it’s whether we normalize spam or we reject it. Is Bitcoin for data storage or financial transactions? https://www.youtube.com/watch?v=15biQH1H140 Every Bitcoiner needs to see this! Vires in Numeris.
A great counterargument by Seth for Privacy:
https://x.com/sethforprivacy/status/1919003009880616976
Personally, I tend to agree with Seth.
To sum it up:
If you are running a node, you should switch from Core to Knots immediately. It's very straightforward, and you don't need to redo the initial block download.
If you arent running a node you are a leech and need to get your shit together.
➡️Tether CEO defends skipping MiCA, calling EU stablecoin rules “very dangerous.” Ardoino: “The European Central Bank is more interested in pushing the digital euro to control people and how they spend their money.”
On the 3rd of May:
➡️Arizona Governor Katie Hobbs has vetoed the state’s Strategic Bitcoin Reserve legislation after it was passed by the House and Senate. She states: “Arizonans’ retirement funds are not the place for the state to try untested investments like virtual currency.”
Apparently, the Arizona State Retirement System already holds 53,097 shares of MSTR. You can’t make this shit up.
➡️Vitalik Buterin: 'One of the best things about Bitcoin is how simple it is. This simplicity has lots of benefits. Let's bring those benefits to Ethereum.' Almost like Bitcoin is eh......(checks notes)......better tech. Just use Bitcoin, dumbfuck! 'It's only taken a decade, but Ethereum's creator is having an inkling that he never should have created Ethereum, which destroyed billions of precious capital and instead focused on Bitcoin.' - Vijay Boyapati
There is no second best!
On the 4th of May:
➡️Eli Nagar:
Heads up, Bitcoin holders: The EU will ban anonymous crypto accounts by July 2027. Every transaction above €1,000 will need your ID. Privacy is becoming extinct. Every new restriction is a marketing campaign for Bitcoin. “Hi, we’re the EU. We’ll surveil you, control your money, and criminalise privacy.” By doing that, they have decided to help promote the black market...great work, EU! Oh, and remember, the EU can't ban what it has no control over: hold your own private keys.
➡️Cumulative inflows into the Bitcoin ETFs have hit a fresh ATH of $ 40.62 B.
On the 5th of May:
➡️Brown University invested $4.9M in Bitcoin via BlackRock's IBIT, as disclosed in a recent SEC filing. The university owns 105K IBIT shares ($5.8M), 2.3% of Brown's reported $216M equity holdings.
➡️Strategy acquires 1,895 BTC for $180.3 million at an average price of $95,167 per bitcoin. As of May 4, 2025, they hold 555,450 BTC acquired for $38.08 billion at an average price of $68,550 per bitcoin.
💸Traditional Finance / Macro:
On the 3rd of May:
👉🏽Berkshire Hathaway cash pile hits record $347.7bn in 1Q as Warren Buffett sells stocks for 10th quarter in a row. Buffett is still raising cash. https://i.ibb.co/1GK6Dvzx/Gq-Bp6q-BW4-AAKKlm.jpg
🏦Banks:
👉🏽 No news
🌎Macro/Geopolitics:
On the 27th of April:
👉🏽World central banks are diversifying their reserves: Foreign holdings of Treasuries as % of US government debt have fallen to ~23%, the lowest in 22 years. The percentage is down ~11 percentage points over the last 9 years. At the same time, gold holdings as a % of global international reserves have hit ~18%, the highest in 26 years. The share has risen by ~8 percentage points since 2015. China has been one of the biggest buyers of gold over the last few years. Since the beginning of 2023, China’s gold reserves as a % of total foreign reserves have doubled to 7.1%.
Everyone wants gold. https://i.ibb.co/NgX11DZh/Gp4-GKc-HWMAAa-FYu.jpg
On the 28th of April:
👉🏽TKL: 'Tariffs are hitting American meat exports.
China's cancellations of US pork shipments are skyrocketing: China cancelled shipments of ~12,000 metric tons of US pork last week, the most since the 2020 pandemic, when global supply chains were halted. As a result, overall US pork export sales dropped to their lowest level since October, according to Bloomberg. This comes as American pork imports to China now face a massive 172% tariff. This includes the duties first imposed during the 2018 trade war.'
On the 29th of April:
👉🏽The U.S. Treasury will now need to borrow $514 billion this quarter, an increase of 320% from its previous estimate.
On the 30th of April:
👉🏽'Bad news for electricity consumers: despite 84 hours of negative pricing (2024: 62 hours), the average electricity price in the Netherlands in April was €75/MWh — nearly 30% higher than a year ago.' - Martien Visser
https://i.ibb.co/VsrFdKy/Gps0l-Au-Xs-AA20-OA.png
👉🏽Tax cuts for the rich lead to higher income inequality. However, they do not have any significant effect on economic growth or unemployment. Empirical evidence for advanced economies over 1965-2015:
https://academic.oup.com/ser/article/20/2/539/6500315?login=false
Trickle down never worked.
👉🏽"Since February 2020, home prices have increased 45%," according to Zillow So has the broad money supply. Not your house is getting more expensive; The money is getting devalued.
Money supply= +40%
Median home= +40%
Experts: "What could have ever caused this????"
And some freaking guru on Instagram or Tiktok is trying to convince you to get his/her 'buying/renting a house' course. https://i.ibb.co/bMXfW3vp/Gp0-CXg-Ka-YAAIhq-J.jpg
👉🏽SUMMARY OF US Q1 GDP REPORT: 1. The U.S. economy contracted at an annual rate of -0.3% in the first quarter, compared to expectations for an increase of 0.2%. That’s down from the growth of 2.4% in Q4. 2. Real consumer spending rose by 1.8% Y/Y, after increasing 4.0% in Q4. 3. The GDP Price Index rose 3.7%, above estimates of 3.1%. 4. Core PCE Prices rose 3.5%, after increasing 2.6% in Q4.
• Key Takeaway: Fears of stagflation are growing as the economy grinds to a halt and inflation ticks higher. - Jesse Cohen
👉🏽World debt has now officially crossed $300 TRILLION, and still continues to climb aggressively. This will not end well…
https://i.ibb.co/Kxm2bJs6/Gpyi-Ouwa-YAEDg-Pq.jpg
👉🏽'March PCE inflation, the Fed's preferred inflation measure, FALLS to 2.3%, above expectations of 2.2%. Core PCE inflation FALLS to 2.6%, in line with expectations of 2.6%. February Core PCE inflation was revised up to 3.0%. All eyes are on the Fed next week.' - TKL
🎁If you have made it this far, I would like to give you a little gift, well, in this case, two gifts:
Smitty's Bitcoin Retirement Guide:
"Helping you develop a better Bitcoin stacking target for life planning." - Sminston With This is a fantastic tool. Very, very useful. I will keep mentioning it. Bitcoin is a savings vehicle. Period!
https://x.com/sminston_with/status/1917605539279954391
The best kind of retirement starts in diapers and ends in diapers, so start now. https://i.ibb.co/4RwFxR0W/Gpys-GQga-YAIxm-MX.jpg
nofinancialadvice
Credit: I have used multiple sources!
My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly.
Use the code SE3997
Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀ ⠀
⠀⠀ ⠀ ⠀⠀⠀
Do you think this post is helpful to you?
If so, please share it and support my work with a zap.
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
⭐ Many thanks⭐
Felipe - Bitcoin Friday!
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
-
 @ aa8de34f:a6ffe696
2025-03-31 21:48:50
@ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht:
„Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ (Quelle: t.me/rosenbusch/25228)
Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität.
-- Denn es braucht keinen Untergrund mehr. --
Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür.
Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung.
Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde.
Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen.
Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit.
Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall.
-
 @ 57d1a264:69f1fee1
2025-05-07 06:29:52
@ 57d1a264:69f1fee1
2025-05-07 06:29:52Your device, your data. TRMNL's architecture prevents outsiders (including us) from accessing your local network. TRMNAL achieve this through 1 way communication between client and server, versus the other way around. Learn more.
Learn more at https://usetrmnl.com/
originally posted at https://stacker.news/items/973632
-
 @ 84b0c46a:417782f5
2025-05-10 07:23:28
@ 84b0c46a:417782f5
2025-05-10 07:23:28- lumilumi The Nostr Web Client.
Lightweight modes are available, such as not displaying icon images, not loading images automatically, etc.
-
Long Form Content Editor A lightweight Long Form Content Editor with editing functionality for your articles. It supports embedding Nostr IDs via NIP-19 and custom emoji integration.
-
nostr-share-component Demo A simple web component for sharing content to Nostr. Create customizable share buttons that let users easily post to Nostr clients with pre-filled content. Perfect for blogs, websites, or any content you want shared on the Nostr network. Try the interactive demo to see how seamlessly it integrates with your website.
-
Nostr Follow Organizer A practical tool for managing your Nostr follows(kind3) with ease.
-
NAKE NAKE is a powerful utility for Nostr developers and users that simplifies working with NIP-19 and NIP-49 formats. This versatile tool allows you to easily encode and decode Nostr identifiers and encrypted data according to these protocol specifications.
- chrome extension
- firefox add-on
-
nostviewstr A versatile Nostr tool that specializes in creating and editing addressable or replaceable events on the Nostr network. This comprehensive editor allows you to manage various types of lists and structured content within the Nostr ecosystem.
-
luminostr Luminostr is a recovery tool for Nostr that helps you retrieve and restore Addressable or Replaceable events (such as kind: 0, 3, 10002, 10000, etc.) from relays. It allows you to search for these events across multiple relays and optionally re-publish them to ensure their persistence.
-
Nostr Bookmark Recovery Tool Nostr Bookmark Recovery Tool is a utility for retrieving and re-publishing past bookmark events ( kind:10003,30001,30003 ) from public relays. Rather than automatically selecting the latest version, it allows users to pick any previous version and overwrite the current one with it. This is useful for restoring a preferred snapshot of your bookmark list.
-
Profile Editor Profile Editor is a simple tool for editing and publishing your Nostr profile (kind: 0 event). It allows you to update fields such as name, display name, picture, and about text, and then publish the updated profile to selected relays.
-
nostr-bookmark-viewer Nostr Bookmark Viewer is a tool for viewing and editing Nostr bookmark events (kind: 10003, 30001, 30003). It allows users to load bookmark data from relays, browse saved posts, and optionally edit and publish their own bookmark lists.
-
Nostr Note Duplicater Nostr Note Duplicater is a tool that rebroadcasts an existing Nostr event from a relay to other selected relays.
-
 @ 318ebaba:9a262eae
2025-05-10 07:19:47
@ 318ebaba:9a262eae
2025-05-10 07:19:47Relays play a crucial role in the Nostr communication protocol, serving as the backbone of its decentralized architecture. Here’s an overview of their functions and significance:
Functions of Nostr Relays
-
Data Storage and Broadcasting: Relays act as intermediaries that store and distribute messages between users. When a user sends a message, it is transmitted to one or more relays, which then broadcast that message to other connected clients. This decentralized approach ensures that no single entity controls the flow of information, enhancing censorship resistance[1][2][6].
-
Interoperability: Users can connect to multiple relays simultaneously, allowing them to access the same content across different applications. This interoperability means that messages can be shared and retrieved from various clients without being tied to a specific platform, promoting a more flexible user experience[4][11].
-
User Control: Anyone can run their own relay, which empowers users to maintain control over their data and interactions. By operating a personal relay, users can ensure that their messages are stored and accessible without relying on third-party services, thus enhancing privacy and security[3][7][11].
-
Performance and Reliability: The performance of a Nostr client can be influenced by the relays it connects to. If a relay is slow or unreliable, it can affect the overall user experience. Users are encouraged to choose or add multiple relays to improve message delivery speed and reliability[7][8][11].
Types of Relays
-
Public and Private Relays: There are both public and private relays available. Public relays are free to use, while private relays may charge fees. Paid relays often provide better performance and reduced spam, as the cost can deter malicious users from flooding the network with unwanted content[6][7][14].
-
Self-Hosted Relays: For those who want maximum control and privacy, setting up a self-hosted relay is an option. This allows users to manage their own data and ensure that their communications are not subject to external censorship or data loss[4][7].
In summary, relays are essential to the Nostr protocol, facilitating decentralized communication by storing, broadcasting, and managing messages across a network of users. They enhance user autonomy, improve performance, and contribute to the overall resilience of the Nostr ecosystem. [1] https://www.voltage.cloud/blog/the-essential-guide-to-nostr-relays [2] https://substack.com/home/post/p-158872714?utm_campaign=post&utm_medium=web [3] https://www.purplerelay.com/how-to-run-a-nostr-relay-a-step-by-step-guide/ [4] https://medium.com/@michael.leigh.stewart/nostr-series-part-3-setting-up-a-relay-6f9ca426e43e [5] https://www.voltage.cloud/blog/understanding-nostr-data-storage-relays-and-decentralization [6] https://www.ccn.com/education/what-is-nostr-and-how-to-start-using-nostr/ [7] https://nostr.how/en/relays [8] https://blog.theya.us/what-is-nostr/ [9] https://www.cointribune.com/en/nostr-pour-les-debutants-tout-ce-que-vous-devez-savoir-sur-le-protocole-2/ [10] https://community.umbrel.com/t/introducing-the-official-nostr-relay-app/11339 [11] https://nostr.com/ [12] https://www.habyb.com/blog/nostr-what-is-this-protocol-and-how-does-it-work/ [13] https://www.reddit.com/r/nostr/comments/15jmhpi/purpose_of_free_vs_paid_relay/ [14] https://nostr.com/relays [15] https://www.reddit.com/r/nostr/comments/115cgcu/whats_the_point_of_adding_more_and_more_relays_do/ [16] https://messari.io/copilot/share/understanding-nostr-f00aa3df-d02c-4381-91f5-9a103b8e25ce
-
-
 @ 4cebd4f5:0ac3ed15
2025-05-10 01:24:16
@ 4cebd4f5:0ac3ed15
2025-05-10 01:24:16TỔNG QUAN HACKATHON
Stellar Build Better Hackathon kết thúc thành công với 220 developervà84 dự ánđược phê duyệt. Sự kiện tập trung ứng dụngsmart contractscủa Stellar vào giải pháp thực tế, thúc đẩy hợp tác cộng đồng và tiến bộ công nghệ. Tổng giải thưởng 25.000 USD (USDC) được phân bổ cho 3 hạng mục: Better Finance (Tài chính tốt hơn), Better Creativity (Sáng tạo tốt hơn) và Better Access (Tiếp cận tốt hơn).
Các developer khám phá nhiều lĩnh vực như công cụ tiếp cận DeFi, giải pháp thanh toán xuyên biên giới, nền tảng cho creator economy, và hệ thống định danh số. Hackathon còn mang đến cơ hội kết nối với developer toàn cầu và các công ty crypto hàng đầu, cùng workshop kỹ thuật và demo trực tiếp.
Thành tựu nổi bật:
-
Giải Nhất (12.000 USDC): Dự án cải thiện tiếp cận tài chính.
-
Giải Nhì (8.000 USDC): Đổi mới công cụ sáng tạo.
-
Giải Ba (5.000 USDC): Giải pháp tiếp cận đột phá.
Sự kiện khẳng định vai trò của Stellar trong thúc đẩy ứng dụng smart contracts mở rộng hệ sinh thái.
CÁC DỰ ÁN ĐOẠT GIẢI
Build Better Prizes
Giải Nhất
PayZoll_Stellar: Tích hợp AI và blockchain trong hệ sinh thái Stellar, cung cấp dịch vụ payroll toàn cầu tự động, minh bạch và bảo mật – nâng cao hiệu quả quản lý lương.Giải Nhì
StellarFinance: Kết nối người dùng với cố vấn tài chính trên blockchain Stellar, đảm bảo dịch vụ tài chính minh bạch, tập trung vào tính toàn vẹn và trải nghiệm người dùng.Giải Ba
Soroban to MCP Server in seconds + Policy Signers Playground: Chuyển đổi smart contracts Soroban (Stellar) thành máy chủ MCP cho tương tác ngôn ngữ tự nhiên, kích hoạt AI agents nâng cao chức năng hợp đồng thông minh.Xem toàn bộ dự án tại DoraHacks.
THÔNG TIN ĐƠN VỊ TỔ CHỨC
Stellar Development Foundation
Tổ chức thúc đẩy phát triển mạng lưới Stellar – nền tảng blockchain tối ưu giao dịch xuyên biên giới. Với trọng tâm DeFi, Stellar triển khai dự án mở rộng tài chính toàn diện toàn cầu. Thông qua mạng lưới đối tác rộng lớn, tổ chức xây dựng giải pháp blockchain mở rộng, đảm bảo khả năng tiếp cận và độ tin cậy cho dịch vụ tài chính. Sứ mệnh của Stellar là kiến tạo cơ hội công bằng trong nền kinh tế toàn cầu qua công nghệ open-source đột phá.
-
-
 @ 318ebaba:9a262eae
2025-05-10 07:06:45
@ 318ebaba:9a262eae
2025-05-10 07:06:45Nostr, which stands for "Notes and Other Stuff Transmitted by Relays," is a decentralized communication protocol designed to facilitate the exchange of messages without relying on centralized servers. This innovative framework allows users to create, broadcast, and receive messages freely, emphasizing user empowerment and censorship resistance.
Key Features of Nostr
-
Decentralization: Unlike traditional social media platforms, Nostr operates on a network of relays, which are servers that anyone can run. This structure eliminates the control that a single entity can exert over the platform, thereby reducing the risk of censorship and enhancing user privacy[1][4][5].
-
Open Protocol: Nostr is not an application itself but a protocol that developers can use to build various applications. This openness allows for a wide range of services, from social media to messaging, all built on the same underlying technology. Users can access multiple applications using a single public/private key pair, making it easier to manage their online identities[2][3][4].
-
Censorship Resistance: One of the primary motivations behind Nostr's creation is to provide a platform where users can communicate without fear of censorship. This is particularly appealing to those disillusioned with traditional social media platforms that often impose restrictions on content[5][10].
-
User Control: Nostr empowers users by allowing them to control their data and interactions. Users can choose which relays to connect to and can run their own relays, ensuring that they are not dependent on any single service provider[4][5][7].
-
Cryptographic Security: The protocol employs public-key cryptography to secure messages and verify identities, similar to how Bitcoin operates. This ensures that messages are authentic and have not been tampered with during transmission[5][10].
Applications and Community
Nostr has gained traction among various communities, particularly within the cryptocurrency space, where figures like Jack Dorsey and Edward Snowden have expressed support for its potential to reshape online communication. The protocol's design allows for a variety of applications, including social media platforms, chat services, and content sharing tools, all of which can interoperate seamlessly[2][3][5].
In summary, Nostr represents a significant shift in how digital communication can be structured, prioritizing decentralization, user autonomy, and resistance to censorship, making it a compelling alternative to conventional social media platforms. [1] https://threenine.blog/posts/what-is-nostr [2] https://www.forbes.com/sites/digital-assets/2023/04/11/how-to-get-started-with-nostr/ [3] https://www.forbes.com/sites/digital-assets/2024/07/17/your-guide-to-nostr-the-decentralized-network-for-everything/ [4] https://www.ledger.com/academy/glossary/nostr [5] https://river.com/learn/what-is-nostr/ [6] https://www.cointribune.com/en/comment-utiliser-nostr-guide-pour-debutants-2/ [7] https://www.ccn.com/education/what-is-nostr-and-how-to-start-using-nostr/ [8] https://nostr.com/ [9] https://mylessnider.com/articles/why-im-excited-about-nostr [10] https://en.wikipedia.org/wiki/Nostr [11] https://nostr.how/en/what-is-nostr [12] https://nostr.org/ [13] https://medium.com/@colaru/an-introduction-to-nostr-protocol-dbc774ac797c [14] https://www.linkedin.com/pulse/what-nostr-manfred-van-doorn-nf9ce [15] https://www.cointribune.com/en/nostr-pour-les-debutants-tout-ce-que-vous-devez-savoir-sur-le-protocole-2/ [16] https://www.reddit.com/r/Bitcoin/comments/17j5glg/do_people_in_this_sub_know_about_nostr/ [17] https://www.voltage.cloud/blog/the-essential-guide-to-nostr-relays [18] https://www.reddit.com/r/nostr/comments/1i6t4g7/explain_how_nostr_works_like_im_a_5_year_old/ [19] https://github.com/nostr-protocol/nostr
-
-
 @ 6830c409:ff17c655
2025-05-10 15:38:09
@ 6830c409:ff17c655
2025-05-10 15:38:09Disclaimer: I used Grammarly AI to correct my poor English to look polished. **
Preface: The motivation behind this note stems from a personal curiosity sparked by a few interactions with someone I know. After watching a YouTube video by Salvaveritate on Narcissistic Personality Disorder, I realized that what I was observing wasn’t purely NPD-it seemed to be intertwined with something else. I wanted to better understand this person’s thought process and what might be driving their behavior. At the end of this note, I’ve included the references I consulted to explore this phenomenon further.
We’ve all encountered that person who walks into a room like they own it-dismissing every idea but their own and expecting the world to revolve around them. There’s confidence, and then there’s a level of self-importance so exaggerated it becomes something darker. That, in a nutshell, is megalomania.
Though it’s no longer a formal psychological diagnosis (now categorized under narcissistic personality disorder), the term “megalomania” still resonates when we describe someone with delusional beliefs about their power, brilliance, or importance. It’s not just arrogance-it’s a complete departure from reality, where self-worth is inflated to cartoonish proportions.
The Many Faces of Megalomania
Megalomaniacs aren’t always easy to spot at first. They can be charismatic, persuasive, and even inspiring-until you begin to notice the patterns. Here are some of the archetypes you might recognize:
-
The Political Power Player: From infamous historical figures to the neighborhood HOA president who rules like a tyrant, these individuals believe only they can save the day.
-
The Corporate Climber: Ambition isn’t the issue here-it’s the willingness to trample anyone in their path. These folks take credit for others' work and treat colleagues like pawns.
-
The Self-Proclaimed Guru: Think of that person who reads one book and suddenly thinks they’ve unlocked the secrets of the universe. They believe they alone hold the truth and must share it with the “less enlightened.”
-
The Everyday Ego: Perhaps the most common. They're the friend who always turns the conversation back to themselves or the family member who demands special treatment at every gathering.
Warning Signs to Watch For
If you suspect someone in your orbit might be leaning into megalomaniac territory, here are some red flags:
- They crave admiration but rarely offer it in return.
- Criticism-even the gentle kind - triggers rage or defensiveness.
- They exaggerate achievements or name-drop to elevate their image.
- Rules are for everyone else - they believe they’re exempt.
- People are merely tools to further their personal agenda.
Often, the charm and confidence they exude can blind you to these signs until you're in too deep. Many learn this lesson through tough workplace dynamics, toxic relationships, or manipulative friendships.
How to Protect Yourself
If you're dealing with a megalomaniac, remember: you’re not powerless. Strategies that actually help include:
- Don't feed the ego - Respectful neutrality works better than flattery.
- Set firm boundaries - Be clear about what is and isn’t acceptable.
- Keep records - Especially in professional settings, documentation is crucial.
- Know when to walk away - Some relationships or environments can’t be fixed.
- Seek support - Therapy can equip you with the tools to cope and recover.
Trying to “change” a megalomaniac rarely works-focus instead on preserving your own mental health and emotional well-being.
A Look Through History-and the Mirror
From Hitler and Stalin’s destructive delusions of grandeur to modern business figures like Elizabeth Holmes, history is packed with cautionary tales of unchecked ego. Even pop culture gives us glimpses: Tony Montana in Scarface, Miranda Priestly in The Devil Wears Prada. These characters aren’t just dramatic-they’re psychological case studies in what happens when ego eclipses empathy.
But let’s be honest-none of us are immune to moments of inflated self-worth. The difference lies in self-awareness. True confidence coexists with humility. It laughs at karaoke fails and learns from criticism. Megalomania, by contrast, builds walls around insecurity and calls it a fortress.
Have you ever dealt with someone whose ego became their identity? Or maybe caught yourself slipping into that territory? Let’s unpack it together-your insights could help someone else recognize the signs early.
Here is what I read: 1. https://ebeni.wordpress.com/unethical-leaders/megalomania-and-narcissism-grandiose-vulnerable-clarke/ 2. https://keghart.org/demirdjian-megalomaniac-dictator/ 3. https://fastercapital.com/content/Megalomania--The-Ultimate-Form-of-Hubris.html 4. https://taylorandfrancis.com/knowledge/Medicine_and_healthcare/Psychiatry/Megalomania/ 5. https://www.encyclopedia.com/medicine/psychology/psychology-and-psychiatry/grandiosity 6. Salva Veritate's video: https://www.youtube.com/watch?v=RtUFB3tf1lA&pp=ygUOc2FsdmEgdmVyaXRhdGU%3D
-
-
 @ 57d1a264:69f1fee1
2025-05-07 06:16:30
@ 57d1a264:69f1fee1
2025-05-07 06:16:30Here’s Sean Voisen writing about how programming is a feeling:
For those of us who enjoy programming, there is a deep satisfaction that comes from solving problems through well-written code, a kind of ineffable joy found in the elegant expression of a system through our favorite syntax. It is akin to the same satisfaction a craftsperson might find at the end of the day after toiling away on well-made piece of furniture, the culmination of small dopamine hits that come from sweating the details on something and getting them just right. Maybe nobody will notice those details, but it doesn’t matter. We care, we notice, we get joy from the aesthetics of the craft.
This got me thinking about the idea of satisfaction in craft. Where does it come from?
Continue Reading https://blog.jim-nielsen.com/2025/craft-and-satisfaction/
originally posted at https://stacker.news/items/973628
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 58d88196:bec81862
2025-05-09 19:22:48
@ 58d88196:bec81862
2025-05-09 19:22:48AI revolution is inevitable.
How to Win Using AI:
AI tools can enhance productivity, creativity, and efficiency. Those who adopt and master AI technologies can outperform others in their field, effectively "winning" by staying ahead. For example: In creative fields: AI can assist with generating ideas, editing, or automating repetitive tasks, allowing professionals to focus on high-value work.
In technical roles: AI can analyze data, optimize processes, or write code faster, giving users an edge.
In business: AI can provide insights through data analysis, improve customer service with chatbots, or streamline operations.
How to Win Using AI: Learn AI Tools: Familiarize yourself with AI platforms relevant to your industry (e.g., ChatGPT for writing, MidJourney for design, or TensorFlow for data science).
Automate Routine Tasks: Use AI to handle repetitive work, freeing up time for strategic thinking.
Enhance Skills: Combine AI with your expertise to produce better results faster—e.g., using AI to draft a report, then refining it with your unique insights.
Stay Competitive: Continuously adapt to new AI advancements to maintain an edge over those who don’t use AI.
-
 @ a5ee4475:2ca75401
2025-05-09 17:39:47
@ a5ee4475:2ca75401
2025-05-09 17:39:47clients #list #descentralismo #english #article #finalversion
*These clients are generally applications on the Nostr network that allow you to use the same account, regardless of the app used, keeping your messages and profile intact.
**However, you may need to meet certain requirements regarding access and account NIP for some clients, so that you can access them securely and use their features correctly.
CLIENTS
Twitter like
- Nostrmo - [source] 🌐🤖🍎💻(🐧🪟🍎)
- Coracle - Super App [source] 🌐
- Amethyst - Super App with note edit, delete and other stuff with Tor [source] 🤖
- Primal - Social and wallet [source] 🌐🤖🍎
- Iris - [source] 🌐🤖🍎
- Current - [source] 🤖🍎
- FreeFrom 🤖🍎
- Openvibe - Nostr and others (new Plebstr) [source] 🤖🍎
- Snort 🌐(🤖[early access]) [onion] [source]
- Damus 🍎 [source]
- Nos 🍎 [source]
- Nostur 🍎 [source]
- NostrBand 🌐 [info] [source]
- Yana 🤖🍎🌐💻(🐧) [source]
- Nostribe [on development] 🌐 [source]
- Lume 💻(🐧🪟🍎) [info] [source]
- Gossip - [source] 💻(🐧🪟🍎)
- Camelus [early access] 🤖 [source]
Communities
- CCNS - Community Curated Nostr Stuff [source]
- noStrudel - Gamified Experience [onion] [info/source] 🌐
- [Nostrudel Next] - [onion]
- moStard - Nostrudel with Monero [onion] [info/source] 🌐
- Nostr Kiwi [creator] 🌐
- Satellite [info] 🌐
- Flotilla - [source] 🌐🐧
- Chachi - [source] 🌐
- Futr - Coded in haskell [source] 🐧 (others soon)
- Soapbox - Comunnity server [info] [source] 🌐
- Ditto - Soapbox comunnity server 🌐 [source] 🌐
- Cobrafuma - Nostr brazilian community on Ditto [info] 🌐
- Zapddit - Reddit like [source] 🌐
- Voyage (Reddit like) [on development] 🤖
Wiki
Search
- Advanced nostr search - Advanced note search by isolated terms related to a npub profile [source] 🌐
- Nos Today - Global note search by isolated terms [info] [source] 🌐
- Nostr Search Engine - API for Nostr clients [source]
- Ntrends - Trending notes and profiles 🌐
Website
App Store
ZapStore - Permitionless App Store [source] 🤖 💻(🐧🍎)
Video and Live Streaming
- Flare - Youtube like 🌐 [source]
- ZapStream - Live streaming and zap who you want (NIP-53) [source] 🤖(on zapstore) 🌐
- Swae - Live streaming [source] (on development) ⏳
Audio and Podcast Transmission
- Castr - Your npub as podcast feed [source]
- Nostr Nests - Audio Chats [source] 🌐
- Fountain - Podcast [source] 🤖🍎
- Corny Chat - Audio Chat [source] 🌐
Music
- Tidal - Music Streaming [source] [about] [info] 🤖🍎🌐
- Wavlake - Music Streaming [source] 🌐(🤖🍎 [early access])
- Tunestr - Musical Events [source] [about] 🌐
- Stemstr - Musical Colab (paid to post) [source] [about] 🌐
Images
- Lumina - Trending images and pictures [source] 🌐
- Pinstr - Pinterest like [source] 🌐
- Slidestr - DeviantArt like [source] 🌐
- Memestr - ifunny like [source] 🌐
Download and Upload
Documents, graphics and tables
- Mindstr - Mind maps [source] 🌐
- Docstr - Share Docs [info] [source] 🌐
- Formstr - Share Forms [info] 🌐
- Sheetstr - Share Spreadsheets [source] 🌐
- Slide Maker - Share slides 🌐 (advice: https://zaplinks.lol/ and https://zaplinks.lol/slides/ sites are down)
Health
- Sobrkey - Sobriety and mental health [source] 🌐
- NosFabrica - Finding ways for your health data 🌐
- LazerEyes - Eye prescription by DM [source] 🌐
Forum
- OddBean - Hacker News like [info] [source] 🌐
- LowEnt - Forum [info] 🌐
- Swarmstr - Q&A / FAQ [info] 🌐
- Staker News - Hacker News like 🌐 [info]
Direct Messenges (DM)
- 0xchat 🤖🍎 [source]
- Nostr Chat 🌐🍎 [source]
- Blowater 🌐 [source]
- Anigma (new nostrgram) - Telegram based [on development] [source]
- Keychat - Signal based [🤖🍎 on development] [source]
Reading
- nRSS - Nostr RSS reader 🌐
- Highlighter - Insights with a highlighted read [info] 🌐
- Zephyr - Calming to Read [info] 🌐
- Flycat - Clean and Healthy Feed [info] 🌐
- Nosta - Check Profiles [on development] [info] 🌐
- Alexandria - e-Reader and Nostr Knowledge Base (NKB) [source] 🌐
Writing
Lists
- Following - Users list [source] 🌐
- Nostr Unfollower - Nostr Unfollower
- Listr - Lists [source] 🌐
- Nostr potatoes - Movies List source 💻(numpy)
Market and Jobs
- Shopstr - Buy and Sell [source] 🌐
- Nostr Market - Buy and Sell 🌐
- Plebeian Market - Buy and Sell [source] 🌐
- Ostrich Work - Jobs [source] 🌐
- Nostrocket - Jobs [source] 🌐
Data Vending Machines - DVM (NIP90)
(Data-processing tools)
Games
- Chesstr - Chess 🌐 [source]
- Jestr - Chess [source] 🌐
- Snakestr - Snake game [source] 🌐
- DEG Mods - Decentralized Game Mods [info] [source] 🌐
- NG Engine - Nostr Game Engine [source] 🌐
- JmonkeyEngine - Java game engine [source] 🌐
Customization
Like other Services
- Olas - Instagram like [source] 🤖🍎🌐
- Nostree - Linktree like 🌐
- Rabbit - TweetDeck like [info] 🌐
- Zaplinks - Nostr links 🌐
- Omeglestr - Omegle-like Random Chats [source] 🌐
General Uses
- Njump - HTML text gateway source 🌐
- Filestr - HTML midia gateway [source] 🌐
- W3 - Nostr URL shortener [source] 🌐
- Playground - Test Nostr filters [source] 🌐
- Spring - Browser 🌐
Places
- Wherostr - Travel and show where you are
- Arc Map (Mapstr) - Bitcoin Map [info]
Driver and Delivery
- RoadRunner - Uber like [on development] ⏱️
- Nostrlivery - iFood like [on development] ⏱️
[⚠️SCAM⚠️] Arcade City - Uber like [source]
OTHER STUFF
Lightning Wallets (zap)
- Alby - Native and extension [info] 🌐
- ZBD - Gaming and Social [info] 🤖🍎
- Wallet of Satoshi [info] 🤖🍎
- Minibits - Cashu mobile wallet [info] 🤖
- Blink - Opensource custodial wallet (KYC over 1000 usd) [source] 🤖🍎
- LNbits - App and extesion [source] 🤖🍎💻
- Zeus - [info] [source] 🤖🍎
Exchange
Media Server (Upload Links)
audio, image and video
Connected with Nostr (NIP):
- Nostr Build - Free and paid Upload [info] [source] 🌐
- NostrMedia - Written in Go with Nip 96 / Blossom (free and paid) [info] [source]
- Nostr Check - [info] [source] 🌐
- NostPic - [info] [source] 🌐
- Sovbit - Free and paid upload [info] [source] 🌐
- Voidcat - Nip-96 and Blossom [source] 🌐
- Primal Media - [source] 🌐
Blossom - Your Media Safer
Primal Blossom 🌐 NostrBuild Blossom - Free upload (max 100MiB) and paid [info] [source] 🌐
Paid Upload Only
Satellite CDN - prepaid upload (max 5GB each) [info] [source] 🌐
Without Nostr NIP:
- Pomf - Upload larger videos (max 1GB) [source]
- Catbox - max 200 MB [source]
- x0 - max 512 MiB [source]
Donation and payments
- Zapper - Easy Zaps [source] 🌐
- Autozap [source] 🌐
- Zapmeacoffee 🌐
- Nostr Zap 💻(numpy)
- Creatr - Creators subscription 🌐
- Geyzer - Crowdfunding [info] [source] 🌐
- Heya! - Crowdfunding [source]
Security
- Secret Border - Generate offline keys 💻(java)
- Umbrel - Your private relay [source] 🌐
Key signing and Extension
- Nowser - Account access keys 📱(🤖🍎) 💻(🐧🍎🪟)
- Nos2x - Account access keys 🌐
- Nsec.app 🌐 [info]
- Lume - [info] [source] 🐧🪟🍎
- Satcom - Share files to discuss - [info] 🌐
- KeysBand - Multi-key signing [source] 🌐
Code
- Nostrify - Share Nostr Frameworks 🌐
- Git Workshop (github like) [experimental] 🌐
- Gitstr (github like) [on development] ⏱️
- Osty [on development] [info] 🌐
- Python Nostr - Python Library for Nostr
- Sybil - Creating, managing and test Nostr events [on development] ⏱️
Relay Check and Cloud
- Nostr Watch - See your relay speed 🌐
- NosDrive - Nostr Relay that saves to Google Drive
Bidges and Getways
- Matrixtr Bridge - Between Matrix & Nostr
- Mostr - Between Nostr & Fediverse
- Nostrss - RSS to Nostr
- Rsslay - Optimized RSS to Nostr [source]
- Atomstr - RSS/Atom to Nostr [source]
Useful Profiles and Trends
nostr-voice - Voice note (just some clients)
NOT RELATED TO NOSTR
Android Keyboards
Personal notes and texts
Front-ends
- Nitter - Twitter / X without your data [source]
- NewPipe - Youtube, Peertube and others, without account & your data [source] 🤖
- Piped - Youtube web without you data [source] 🌐
Other Services
- Brave - Browser [source]
- DuckDuckGo - Search [source]
- LLMA - Meta - Meta open source AI [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Proton Mail - Mail [source]
Other open source index: Degoogled Apps
Some other Nostr index on:
-
 @ 57d1a264:69f1fee1
2025-05-07 06:03:29
@ 57d1a264:69f1fee1
2025-05-07 06:03:29CryptPad
Collaboration and privacy. Yes, you can have both Flagship instance of CryptPad, the end-to-end encrypted and open-source collaboration suite. Cloud administered by the CryptPad development team. https://cryptpad.fr/
ONLYOFFICE DocSpace
Document collaboration made simpler. Easily collaborate with customizable rooms. Edit any content you have. Work faster using AI assistants. Protect your sensitive business data. Download or try STARTUP Cloud (Limited-time offer) FREE https://www.onlyoffice.com/
SeaFile
A new way to organize your files Beyond just syncing and sharing files, Seafile lets you add custom file properties and organize your files in different views. With AI-powered automation for generating properties, Seafile offers a smarter, more efficient way to manage your files. Try it Now, Free for up to 3 users https://seafile.com/
SandStorm
An open source platform for self-hosting web apps Self-host web-based productivity apps easily and securely. Sandstorm is an open source project built by a community of volunteers with the goal of making it really easy to run open source web applications. Try the Demo or Signup Free https://alpha.sandstorm.io/apps
NextCloud Hub
A new generation of online collaboration that puts you in control. Nextcloud offers a modern, on premise content collaboration platform with real-time document editing, video chat & groupware on mobile, desktop and web. Sign up for a free Nextcloud account https://nextcloud.com/sign-up/
LinShare
True Open Source Secure File Sharing Solution We are committed to providing a reliable Open Source file-sharing solution, expertly designed to meet the highest standards of diverse industries, such as government and finance Try the Demo https://linshare.app/
Twake Drive
The open-source alternative to Google Drive. Privacy-First Open Source Workplace. Twake workplace open source business. Improve your effeciency with truly Open Source, all-in-one digital suite. Enhance the security in every aspect of your professional and private life. Sign up https://sign-up.twake.app/
SpaceDrive
One Explorer. All Your Files. Unify files from all your devices and clouds into a single, easy-to-use explorer. Designed for creators, hoarders and the painfully disorganized. Download desktop app (mobile coming soon) https://www.spacedrive.com/
ente
Safe Home for your photos Store, share, and discover your memories with end-to-end encryption. End-to-end encryption, durable storage and simple sharing. Packed with these and much more into our beautiful open source apps. Get started https://web.ente.io
fileStash
Turn your FTP server into... Filestash is the enterprise-grade file manager connecting your storage with your identity provider and authorisations. Try the demo https://demo.filestash.app
STORJ
Disruptively fast. Globally secure. S3-compatible distributed cloud services that make the most demanding workflows fast and affordable. Fast track your journey toward high performance cloud services. Storj pricing is consistent and competitive in meeting or exceeding your cloud services needs. Give the products a try to experience the benefits of the distributed cloud. Get Started https://www.storj.io/get-started
FireFile
The open‑source alternative to Dropbox. Firefiles lets you setup a cloud drive with the backend of your choice and lets you seamlessly manage your files across multiple providers. It revolutionizes cloud storage management by offering a unified platform for all your storage needs. Sign up Free https://beta.firefiles.app
originally posted at https://stacker.news/items/973626
-
 @ 7459d333:f207289b
2025-05-10 17:41:17
@ 7459d333:f207289b
2025-05-10 17:41:17Come to our meetup to discuss the great Bitcoin Core debate!
The proposal to remove the 80-byte limit on OP_RETURN is getting people talking: should Bitcoin prioritize only monetary transactions or allow more data, such as notarizations?
Some argue that this simplifies the protocol and reflects what already happens in practice, with data stuffed in less efficient ways (as in Taproot).
Others fear it will overload the blockchain and take Bitcoin away from its essence....
Bring your opinion, enjoy a beer and let's debate the future of Bitcoin!
https://t.me/madridmeetup
originally posted at https://stacker.news/items/976659
-
 @ a008def1:57a3564d
2025-04-30 17:52:11
@ a008def1:57a3564d
2025-04-30 17:52:11A Vision for #GitViaNostr
Git has long been the standard for version control in software development, but over time, we has lost its distributed nature. Originally, Git used open, permissionless email for collaboration, which worked well at scale. However, the rise of GitHub and its centralized pull request (PR) model has shifted the landscape.
Now, we have the opportunity to revive Git's permissionless and distributed nature through Nostr!
We’ve developed tools to facilitate Git collaboration via Nostr, but there are still significant friction that prevents widespread adoption. This article outlines a vision for how we can reduce those barriers and encourage more repositories to embrace this approach.
First, we’ll review our progress so far. Then, we’ll propose a guiding philosophy for our next steps. Finally, we’ll discuss a vision to tackle specific challenges, mainly relating to the role of the Git server and CI/CD.
I am the lead maintainer of ngit and gitworkshop.dev, and I’ve been fortunate to work full-time on this initiative for the past two years, thanks to an OpenSats grant.
How Far We’ve Come
The aim of #GitViaNostr is to liberate discussions around code collaboration from permissioned walled gardens. At the core of this collaboration is the process of proposing and applying changes. That's what we focused on first.
Since Nostr shares characteristics with email, and with NIP34, we’ve adopted similar primitives to those used in the patches-over-email workflow. This is because of their simplicity and that they don’t require contributors to host anything, which adds reliability and makes participation more accessible.
However, the fork-branch-PR-merge workflow is the only model many developers have known, and changing established workflows can be challenging. To address this, we developed a new workflow that balances familiarity, user experience, and alignment with the Nostr protocol: the branch-PR-merge model.
This model is implemented in ngit, which includes a Git plugin that allows users to engage without needing to learn new commands. Additionally, gitworkshop.dev offers a GitHub-like interface for interacting with PRs and issues. We encourage you to try them out using the quick start guide and share your feedback. You can also explore PRs and issues with gitplaza.
For those who prefer the patches-over-email workflow, you can still use that approach with Nostr through gitstr or the
ngit sendandngit listcommands, and explore patches with patch34.The tools are now available to support the core collaboration challenge, but we are still at the beginning of the adoption curve.
Before we dive into the challenges—such as why the Git server setup can be jarring and the possibilities surrounding CI/CD—let’s take a moment to reflect on how we should approach the challenges ahead of us.
Philosophy
Here are some foundational principles I shared a few years ago:
- Let Git be Git
- Let Nostr be Nostr
- Learn from the successes of others
I’d like to add one more:
- Embrace anarchy and resist monolithic development.
Micro Clients FTW
Nostr celebrates simplicity, and we should strive to maintain that. Monolithic developments often lead to unnecessary complexity. Projects like gitworkshop.dev, which aim to cover various aspects of the code collaboration experience, should not stifle innovation.
Just yesterday, the launch of following.space demonstrated how vibe-coded micro clients can make a significant impact. They can be valuable on their own, shape the ecosystem, and help push large and widely used clients to implement features and ideas.
The primitives in NIP34 are straightforward, and if there are any barriers preventing the vibe-coding of a #GitViaNostr app in an afternoon, we should work to eliminate them.
Micro clients should lead the way and explore new workflows, experiences, and models of thinking.
Take kanbanstr.com. It provides excellent project management and organization features that work seamlessly with NIP34 primitives.
From kanban to code snippets, from CI/CD runners to SatShoot—may a thousand flowers bloom, and a thousand more after them.
Friction and Challenges
The Git Server
In #GitViaNostr, maintainers' branches (e.g.,
master) are hosted on a Git server. Here’s why this approach is beneficial:- Follows the original Git vision and the "let Git be Git" philosophy.
- Super efficient, battle-tested, and compatible with all the ways people use Git (e.g., LFS, shallow cloning).
- Maintains compatibility with related systems without the need for plugins (e.g., for build and deployment).
- Only repository maintainers need write access.
In the original Git model, all users would need to add the Git server as a 'git remote.' However, with ngit, the Git server is hidden behind a Nostr remote, which enables:
- Hiding complexity from contributors and users, so that only maintainers need to know about the Git server component to start using #GitViaNostr.
- Maintainers can easily swap Git servers by updating their announcement event, allowing contributors/users using ngit to automatically switch to the new one.
Challenges with the Git Server
While the Git server model has its advantages, it also presents several challenges:
- Initial Setup: When creating a new repository, maintainers must select a Git server, which can be a jarring experience. Most options come with bloated social collaboration features tied to a centralized PR model, often difficult or impossible to disable.
-
Manual Configuration: New repositories require manual configuration, including adding new maintainers through a browser UI, which can be cumbersome and time-consuming.
-
User Onboarding: Many Git servers require email sign-up or KYC (Know Your Customer) processes, which can be a significant turn-off for new users exploring a decentralized and permissionless alternative to GitHub.
Once the initial setup is complete, the system works well if a reliable Git server is chosen. However, this is a significant "if," as we have become accustomed to the excellent uptime and reliability of GitHub. Even professionally run alternatives like Codeberg can experience downtime, which is frustrating when CI/CD and deployment processes are affected. This problem is exacerbated when self-hosting.
Currently, most repositories on Nostr rely on GitHub as the Git server. While maintainers can change servers without disrupting their contributors, this reliance on a centralized service is not the decentralized dream we aspire to achieve.
Vision for the Git Server
The goal is to transform the Git server from a single point of truth and failure into a component similar to a Nostr relay.
Functionality Already in ngit to Support This
-
State on Nostr: Store the state of branches and tags in a Nostr event, removing reliance on a single server. This validates that the data received has been signed by the maintainer, significantly reducing the trust requirement.
-
Proxy to Multiple Git Servers: Proxy requests to all servers listed in the announcement event, adding redundancy and eliminating the need for any one server to match GitHub's reliability.
Implementation Requirements
To achieve this vision, the Nostr Git server implementation should:
-
Implement the Git Smart HTTP Protocol without authentication (no SSH) and only accept pushes if the reference tip matches the latest state event.
-
Avoid Bloat: There should be no user authentication, no database, no web UI, and no unnecessary features.
-
Automatic Repository Management: Accept or reject new repositories automatically upon the first push based on the content of the repository announcement event referenced in the URL path and its author.
Just as there are many free, paid, and self-hosted relays, there will be a variety of free, zero-step signup options, as well as self-hosted and paid solutions.
Some servers may use a Web of Trust (WoT) to filter out spam, while others might impose bandwidth or repository size limits for free tiers or whitelist specific npubs.
Additionally, some implementations could bundle relay and blossom server functionalities to unify the provision of repository data into a single service. These would likely only accept content related to the stored repositories rather than general social nostr content.
The potential role of CI / CD via nostr DVMs could create the incentives for a market of highly reliable free at the point of use git servers.
This could make onboarding #GitViaNostr repositories as easy as entering a name and selecting from a multi-select list of Git server providers that announce via NIP89.
!(image)[https://image.nostr.build/badedc822995eb18b6d3c4bff0743b12b2e5ac018845ba498ce4aab0727caf6c.jpg]
Git Client in the Browser
Currently, many tasks are performed on a Git server web UI, such as:
- Browsing code, commits, branches, tags, etc.
- Creating and displaying permalinks to specific lines in commits.
- Merging PRs.
- Making small commits and PRs on-the-fly.
Just as nobody goes to the web UI of a relay (e.g., nos.lol) to interact with notes, nobody should need to go to a Git server to interact with repositories. We use the Nostr protocol to interact with Nostr relays, and we should use the Git protocol to interact with Git servers. This situation has evolved due to the centralization of Git servers. Instead of being restricted to the view and experience designed by the server operator, users should be able to choose the user experience that works best for them from a range of clients. To facilitate this, we need a library that lowers the barrier to entry for creating these experiences. This library should not require a full clone of every repository and should not depend on proprietary APIs. As a starting point, I propose wrapping the WASM-compiled gitlib2 library for the web and creating useful functions, such as showing a file, which utilizes clever flags to minimize bandwidth usage (e.g., shallow clone, noblob, etc.).
This approach would not only enhance clients like gitworkshop.dev but also bring forth a vision where Git servers simply run the Git protocol, making vibe coding Git experiences even better.
song
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 created song with a complementary vision that has shaped how I see the role of the git server. Its a self-hosted, nostr-permissioned git server with a relay baked in. Its currently a WIP and there are some compatability with ngit that we need to work out.
We collaborated on the nostr-permissioning approach now reflected in nip34.
I'm really excited to see how this space evolves.
CI/CD
Most projects require CI/CD, and while this is often bundled with Git hosting solutions, it is currently not smoothly integrated into #GitViaNostr yet. There are many loosely coupled options, such as Jenkins, Travis, CircleCI, etc., that could be integrated with Nostr.
However, the more exciting prospect is to use DVMs (Data Vending Machines).
DVMs for CI/CD
Nostr Data Vending Machines (DVMs) can provide a marketplace of CI/CD task runners with Cashu for micro payments.
There are various trust levels in CI/CD tasks:
- Tasks with no secrets eg. tests.
- Tasks using updatable secrets eg. API keys.
- Unverifiable builds and steps that sign with Android, Nostr, or PGP keys.
DVMs allow tasks to be kicked off with specific providers using a Cashu token as payment.
It might be suitable for some high-compute and easily verifiable tasks to be run by the cheapest available providers. Medium trust tasks could be run by providers with a good reputation, while high trust tasks could be run on self-hosted runners.
Job requests, status, and results all get published to Nostr for display in Git-focused Nostr clients.
Jobs could be triggered manually, or self-hosted runners could be configured to watch a Nostr repository and kick off jobs using their own runners without payment.
But I'm most excited about the prospect of Watcher Agents.
CI/CD Watcher Agents
AI agents empowered with a NIP60 Cashu wallet can run tasks based on activity, such as a push to master or a new PR, using the most suitable available DVM runner that meets the user's criteria. To keep them running, anyone could top up their NIP60 Cashu wallet; otherwise, the watcher turns off when the funds run out. It could be users, maintainers, or anyone interested in helping the project who could top up the Watcher Agent's balance.
As aluded to earlier, part of building a reputation as a CI/CD provider could involve running reliable hosting (Git server, relay, and blossom server) for all FOSS Nostr Git repositories.
This provides a sustainable revenue model for hosting providers and creates incentives for many free-at-the-point-of-use hosting providers. This, in turn, would allow one-click Nostr repository creation workflows, instantly hosted by many different providers.
Progress to Date
nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr and nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 have been working on a runner that uses GitHub Actions YAML syntax (using act) for the dvm-cicd-runner and takes Cashu payment. You can see example runs on GitWorkshop. It currently takes testnuts, doesn't give any change, and the schema will likely change.
Note: The actions tab on GitWorkshop is currently available on all repositories if you turn on experimental mode (under settings in the user menu).
It's a work in progress, and we expect the format and schema to evolve.
Easy Web App Deployment
For those disapointed not to find a 'Nostr' button to import a git repository to Vercel menu: take heart, they made it easy. vercel.com_import_options.png there is a vercel cli that can be easily called in CI / CD jobs to kick of deployments. Not all managed solutions for web app deployment (eg. netlify) make it that easy.
Many More Opportunities
Large Patches via Blossom
I would be remiss not to mention the large patch problem. Some patches are too big to fit into Nostr events. Blossom is perfect for this, as it allows these larger patches to be included in a blossom file and referenced in a new patch kind.
Enhancing the #GitViaNostr Experience
Beyond the large patch issue, there are numerous opportunities to enhance the #GitViaNostr ecosystem. We can focus on improving browsing, discovery, social and notifications. Receiving notifications on daily driver Nostr apps is one of the killer features of Nostr. However, we must ensure that Git-related notifications are easily reviewable, so we don’t miss any critical updates.
We need to develop tools that cater to our curiosity—tools that enable us to discover and follow projects, engage in discussions that pique our interest, and stay informed about developments relevant to our work.
Additionally, we should not overlook the importance of robust search capabilities and tools that facilitate migrations.
Concluding Thoughts
The design space is vast. Its an exciting time to be working on freedom tech. I encourage everyone to contribute their ideas and creativity and get vibe-coding!
I welcome your honest feedback on this vision and any suggestions you might have. Your insights are invaluable as we collaborate to shape the future of #GitViaNostr. Onward.
Contributions
To conclude, I want to acknowledge some the individuals who have made recent code contributions related to #GitViaNostr:
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 (gitstr, song, patch34), nostr:npub1useke4f9maul5nf67dj0m9sq6jcsmnjzzk4ycvldwl4qss35fvgqjdk5ks (gitplaza)
nostr:npub1elta7cneng3w8p9y4dw633qzdjr4kyvaparuyuttyrx6e8xp7xnq32cume (ngit contributions, git-remote-blossom),nostr:npub16p8v7varqwjes5hak6q7mz6pygqm4pwc6gve4mrned3xs8tz42gq7kfhdw (SatShoot, Flotilla-Budabit), nostr:npub1ehhfg09mr8z34wz85ek46a6rww4f7c7jsujxhdvmpqnl5hnrwsqq2szjqv (Flotilla-Budabit, Nostr Git Extension), nostr:npub1ahaz04ya9tehace3uy39hdhdryfvdkve9qdndkqp3tvehs6h8s5slq45hy (gnostr and experiments), and others.
nostr:npub1uplxcy63up7gx7cladkrvfqh834n7ylyp46l3e8t660l7peec8rsd2sfek (git-remote-nostr)
Project Management nostr:npub1ltx67888tz7lqnxlrg06x234vjnq349tcfyp52r0lstclp548mcqnuz40t (kanbanstr) Code Snippets nostr:npub1ygzj9skr9val9yqxkf67yf9jshtyhvvl0x76jp5er09nsc0p3j6qr260k2 (nodebin.io) nostr:npub1r0rs5q2gk0e3dk3nlc7gnu378ec6cnlenqp8a3cjhyzu6f8k5sgs4sq9ac (snipsnip.dev)
CI / CD nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr
and for their nostr:npub1c03rad0r6q833vh57kyd3ndu2jry30nkr0wepqfpsm05vq7he25slryrnw nostr:npub1qqqqqq2stely3ynsgm5mh2nj3v0nk5gjyl3zqrzh34hxhvx806usxmln03 and nostr:npub1l5sga6xg72phsz5422ykujprejwud075ggrr3z2hwyrfgr7eylqstegx9z for their testing, feedback, ideas and encouragement.
Thank you for your support and collaboration! Let me know if I've missed you.
-
 @ ba3b4b1d:eadff0d3
2025-05-09 23:53:41
@ ba3b4b1d:eadff0d3
2025-05-09 23:53:41Existem seres do tipo "troll" no folclore Português conhecidos como Trasgos, semelhantes a gnomos e duendes. Na interpretação da Vanessa Fidalgo, duende e trasgo seriam sinónimos e ela descreve-os como sendo "refilões, rebeldes, de pequena estatura, nariz arrebatado, tez rugosa, e o povo chama-lhes trasgos ou maruxinhos, que é como quem diz, duendes!"
Escondem-se nas florestas rurais e são famosos por pregar partidas aos viajantes, especialmente aos pastores de ovelhas. Essas criaturas anãs podem aparecer nas lareiras e tornar-se bastante invasivas. Mesmo que alguém se mude de casa, os Trasgos seguem-nos até ao novo lar. Existem rituais que, alegadamente, conseguem expulsar os Trasgos de uma casa.
A natureza jovial e traquina destes seres está relacionada com um Fadário Galego, em que se acreditava que eles eram resultado de crianças que morriam novas, em que a alma ficava presa a uma casa ou a um local agrícola relacionado com a família.
No folclore leonês, são chamados de Trasgos. No folclore castelhano e aragonês, são conhecidos como Martinitos.

Nas Astúrias, o trasgo é conhecido por nomes diferentes, dependendo da localização. Ele é conhecido como Trasno, Cornín ou Xuan Dos Camíos nas Astúrias ocidentais. Ele é conhecido como Gorretín Colorau ou aquele com o "gorro encarnado" (ambos significando "pequeno chapéu vermelho"), nas Astúrias orientais.
Na mitologia Celta, são conhecidos por "Far Darrig" que significa "homem vermelho".
Algumas interpretações sugerem que encarna a natureza caprichosa do destino, lembrando os humanos da imprevisibilidade da jornada da vida. Outras vêem-no como uma representação dos aspectos selvagens e indomáveis do mundo natural, existindo nas margens da compreensão humana.
-
 @ 04c915da:3dfbecc9
2025-03-12 15:30:46
@ 04c915da:3dfbecc9
2025-03-12 15:30:46Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ ba3b4b1d:eadff0d3
2025-05-09 23:51:07
@ ba3b4b1d:eadff0d3
2025-05-09 23:51:07Outro indício de que as relações entre Celtas e Ibéros não foi unilateral é a existência em solo Irlandês da planta Erica mackaiana, conhecida como Urze Galego ou Asturiano
Esta é uma espécie de urze encontrada exclusivamente nas costas da Galiza, Irlanda, Astúrias e Cantábria. Estas plantas estão sempre localizadas a menos de 10 km das margens, na proximidade de povoações costeiras da Idade do Ferro.
Não são nativas da Irlanda. Há indícios que sugerem que muitas espécies da fauna hiberno-lusitana chegaram à Irlanda devido a uma intensa actividade comercial exclusivamente marítima. Por exemplo, a Erica erigena, originalmente nativa da Gália e da Hispânia, é teoricamente considerada como tendo sido transplantada para solo irlandês através do comércio de vinho galaico.
Os indícios de contrabando de E. mackiana incluem o facto de serem encontradas apenas em portos que levam a rotas interiores e em baías isoladas. O local com a maior concentração desta espécie é o Pântano de Roundstone, situado entre duas enseadas isoladas, atravessado por uma antiga estrada de Connemara, uma área com uma longa história de contrabando. Em Kerry, há uma estrada conhecida como Trilho dos Contrabandistas, que foi a principal área de distribuição desta espécie.

-
 @ a3c6f928:d45494fb
2025-05-09 17:21:32
@ a3c6f928:d45494fb
2025-05-09 17:21:32Freedom—a word that resonates deeply within the hearts of many. It is a concept that transcends cultures, boundaries, and time itself. From the pages of history to the hopes of future generations, the quest for freedom has always been at the core of human existence.
What Is Freedom?
At its simplest, freedom is the power or right to act, speak, or think as one wants without hindrance or restraint. But in reality, it is far more nuanced. Freedom is not just about the absence of oppression; it is about the presence of opportunity—the chance to pursue one's dreams, express thoughts without fear, and live in harmony with one’s beliefs.
The Many Faces of Freedom
-
Political Freedom: The right to participate in governance, to vote, and to have a voice in decision-making.
-
Economic Freedom: The ability to work, own property, and engage in business without unreasonable restrictions.
-
Social Freedom: The acceptance of diversity and the ability to live without discrimination.
-
Personal Freedom: The right to privacy, personal choices, and the liberty to define one's own path.
Why Freedom Matters
Freedom matters because it is the foundation of innovation and progress. Societies that encourage freedom allow their people to think differently, to challenge the status quo, and to bring about change. Without freedom, creativity is stifled, voices are silenced, and growth becomes stagnant.
Protecting and Valuing Freedom
Freedom is fragile. It must be protected with vigilance and cherished with gratitude. History is filled with examples where freedom was hard-won and even harder to maintain. Today, as we navigate an interconnected world, the call to safeguard freedom is as loud as ever.
A Call to Action
Cherish your freedoms, no matter how small they may seem. Speak up for those who cannot. Stand firm against injustice. Remember, freedom is not just a privilege; it is a responsibility.
“Freedom is never voluntarily given by the oppressor; it must be demanded by the oppressed.” — Martin Luther King Jr.
Embrace it. Protect it. Share it.
-
-
 @ 6fbc5b6b:0251e3df
2025-05-09 15:46:24
@ 6fbc5b6b:0251e3df
2025-05-09 15:46:24Since its TGE, AGT has moved beyond its early role as a governance token within AIVille’s farming economy. It’s now evolving into a foundational asset that connects humans and AI agents, in-game interactions and real-world use cases. This isn’t just the next phase of a game—it’s the beginning of a new era where intelligent agents and humans co-create a living digital society. Here’s how AGT is becoming the fuel behind that future.
- AI Characters as Personalized Companions The first example of this transformation is Selena, AIVille’s Telegram-native AI companion. You can chat with her now for free at @Tavern_Owner_Selena_Bot. Selena is powered by her own independent memory system, enabling personalized, emotionally responsive conversations that evolve over time. Beyond private chats, Selena also participates in public community groups—responding to questions, engaging with users, and providing companionship in group settings. She’s more than a chatbot—she’s a social presence in the AIVille ecosystem. While currently free to use, certain advanced features and extended interactions will soon require AGT, making Selena a live demonstration of AGT’s role in unlocking real AI experiences.
More characters are on the way: Owen, your AI tutor for learning AI tools, coding basics, or advanced Web3 mechanics. Lulu, your personalized news curator—think of her as your intelligent Substack. Mayor Logan, offering town updates, strategic insights, and even mock governance simulations. Arjay, the town’s resident DJ, creating mood-based playlists you can reserve with AGT. Lucas, a merchant bot offering market tips, negotiation roleplay, and trend forecasting.
Each character is built with private memory and a distinct personality. Interacting with them isn't just fun—it creates lasting, evolving relationships. AGT unlocks deeper access.
- AI Bots for Projects: The AIVille Co-Creation Program We’re launching the AI Co-Creation Program, designed for Web3 projects to easily spin up custom AI bots with memory and personality. These bots can support communities, onboard users, answer questions, or drive engagement—and they’re powered by AGT.
The setup is quick, the AGT required is minimal, and most importantly, participating projects become part of the AIVille ecosystem. AGT serves as the bridge—not just a fee, but a commitment to shared growth. We’re actively testing with partners now. If you’re building in Web3 and want to add a smart, persistent AI layer to your project, reach out. We’re also recruiting global ambassadors: connect a project and help them onboard, and you’ll earn AGT rewards. All AGT from these partnerships is injected into the AIVille DAO, where it will be allocated transparently for buybacks, ecosystem incentives, and long-term development.
- Governance, Reimagined: A Society of Humans and Agents AIVille is introducing a two-layer governance model—one for human players, and one for AI agents. Together, they’ll shape the rules of the world. Human Governance AGT holders will be able to: Propose and vote on decisions like tax rates, new zones, and fee structures Stake AGT to unlock governance perks and exclusive features Fund public goods with DAO-managed AGT reserves Participate in a transparent system where influence is earned, not assumed
AI Economic Alliance In parallel, key AI agents—like Logan, Lucas, and Arjay—will be able to propose changes, backed by AGT. Each proposal requires AGT to be burned as a bond
Passed proposals return a portion; failed ones are fully burned
Humans can vote to support or reject AI proposals, creating real-time, inter-agent governance dynamics
This is more than a voting system—it’s an experiment in social architecture between multiple intelligent actors. And AGT is the trust layer between them.
- What AGT Really Represents AGT isn’t just a token. It’s shared infrastructure. It’s programmable social capital. It’s the backbone of a digital civilization co-created by its users.
It’s how you teach an AI. How you shape the economy. How you reserve access, express values, and coordinate effort. This asset isn’t owned by a company or foundation—it’s governed, used, and grown by the people and agents who rely on it. Our roadmap includes expanding AI services, adding more governance mechanisms, and welcoming more ecosystems into the fold. Every new use case makes AGT more valuable, more usable, and more alive.
- To Our Community: Thank You AGT wouldn’t be here without the people behind it: The AMA hosts introducing AIVille to new audiences The meme creators, sticker designers, and shirt printers The Discord mods, Telegram helpers, and wiki writers
You made this real before the tech did. You gave it soul before it had memory. This isn’t our experiment. It’s yours. Let’s keep building—together.
-
 @ 0c469779:4b21d8b0
2025-03-11 10:52:49
@ 0c469779:4b21d8b0
2025-03-11 10:52:49Sobre el amor
Mi percepción del amor cambió con el tiempo. Leer literatura rusa, principalmente a Dostoevsky, te cambia la perspectiva sobre el amor y la vida en general.
Por mucho tiempo mi visión sobre la vida es que la misma se basa en el sufrimiento: también la Biblia dice esto. El amor es igual, en el amor se sufre y se banca a la otra persona. El problema es que hay una distinción de sufrimientos que por mucho tiempo no tuve en cuenta. Está el sufrimiento del sacrificio y el sufrimiento masoquista. Para mí eran indistintos.
Para mí el ideal era Aliosha y Natasha de Humillados y Ofendidos: estar con alguien que me amase tanto como Natasha a Aliosha, un amor inclusive autodestructivo para Natasha, pero real. Tiene algo de épico, inalcanzable. Un sufrimiento extremo, redentor, es una vara altísima que en la vida cotidiana no se manifiesta. O el amor de Sonia a Raskolnikov, quien se fue hasta Siberia mientras estuvo en prisión para que no se quede solo en Crimen y Castigo.
Este es el tipo de amor que yo esperaba. Y como no me pasó nada tan extremo y las situaciones que llegan a ocurrir en mi vida están lejos de ser tan extremas, me parecía hasta poco lo que estaba pidiendo y que nadie pueda quedarse conmigo me parecía insuficiente.
Ahora pienso que el amor no tiene por qué ser así. Es un pensamiento nuevo que todavía estoy construyendo, y me di cuenta cuando fui a la iglesia, a pesar de que no soy cristiano. La filosofía cristiana me gusta. Va conmigo. Tiene un enfoque de humildad, superación y comunidad que me recuerda al estoicismo.
El amor se trata de resaltar lo mejor que hay en el otro. Se trata de ser un plus, de ayudar. Por eso si uno no está en su mejor etapa, si no se está cómodo con uno mismo, no se puede amar de verdad. El amor empieza en uno mismo.
Los libros son un espejo, no necesariamente vas a aprender de ellos, sino que te muestran quién sos. Resaltás lo que te importa. Por eso a pesar de saber los tipos de amores que hay en los trabajos de Dostoevsky, cometí los mismos errores varias veces.
Ser mejor depende de uno mismo y cada día se pone el granito de arena.
-
 @ 57d1a264:69f1fee1
2025-05-06 06:00:25
@ 57d1a264:69f1fee1
2025-05-06 06:00:25Album art didn’t always exist. In the early 1900s, recorded music was still a novelty, overshadowed by sales of sheet music. Early vinyl records were vastly different from what we think of today: discs were sold individually and could only hold up to four minutes of music per side. Sometimes, only one side of the record was used. One of the most popular records of 1910, for example, was “Come, Josephine, in My Flying Machine”: it clocked in at two minutes and 39 seconds.
The invention of album art can get lost in the story of technological mastery. But among all the factors that contributed to the rise of recorded music, it stands as one of the few that was wholly driven by creators themselves. Album art — first as marketing material, then as pure creative expression — turned an audio-only medium into a multi-sensory experience.
This is the story of the people who made music visible.
originally posted at https://stacker.news/items/972642
-
 @ b99efe77:f3de3616
2025-05-10 14:26:24
@ b99efe77:f3de3616
2025-05-10 14:26:24asfadfadsf draft
afasdfasdfsadf
petrinet ;startDay () -> working ;stopDay working -> () ;startPause working -> paused ;endPause paused -> working ;goSmoke working -> smoking ;endSmoke smoking -> working ;startEating working -> eating ;stopEating eating -> working ;startCall working -> onCall ;endCall onCall -> working ;startMeeting working -> inMeetinga ;endMeeting inMeeting -> working ;logTask working -> working -
 @ 4857600b:30b502f4
2025-03-11 01:58:19
@ 4857600b:30b502f4
2025-03-11 01:58:19Key Findings
- Researchers at the University of Cambridge discovered that aspirin can help slow the spread of certain cancers, including breast, bowel, and prostate cancers
- The study was published in the journal Nature
How Aspirin Works Against Cancer
- Aspirin blocks thromboxane A2 (TXA2), a chemical produced by blood platelets
- TXA2 normally weakens T cells, which are crucial for fighting cancer
- By inhibiting TXA2, aspirin "unleashes" T cells to more effectively target and destroy cancer cells
Supporting Evidence
- Previous studies showed regular aspirin use was linked to:
- 31% reduction in cancer-specific mortality in breast cancer patients
- 9% decrease in recurrence/metastasis risk
- 25% reduction in colon cancer risk
Potential Impact
- Aspirin could be particularly effective in early stages of cancer
- It may help prevent metastasis, which causes 90% of cancer fatalities
- As an inexpensive treatment, it could be more accessible globally than antibody-based therapies
Cautions
- Experts warn against self-medicating with aspirin
- Potential risks include internal bleeding and stomach ulcers
- Patients should consult doctors before starting aspirin therapy
Next Steps
- Large-scale clinical trials to determine which cancer types and patients would benefit most
- Development of new drugs that mimic aspirin's benefits without side effects
Citations: Natural News
-
 @ ba3b4b1d:eadff0d3
2025-05-09 23:49:24
@ ba3b4b1d:eadff0d3
2025-05-09 23:49:24Aisling é um género literário que se tornou popular na Irlanda nos séculos XVII e XVIII depois do tumulto da Guerra Williamita, misturando elementos de folclore, nacionalismo e romantismo. Ela encapsulava um anseio por identidade e liberdade, utilizando a figura da mulher bela como um poderoso símbolo de esperança e aspiração.
Mas a história da Aisling não começa aí e uma das suas origens é o conto muito confuso de Caer Ibormeith, também conhecida por Coerabar Boeth.
(https://yakihonne.s3.ap-east-1.amazonaws.com/ba3b4b1d1c5cc2707f71924368a7adcded1829921c86e022f1cb8117eadff0d3/files/1746834499215-YAKIHONNES3.jpg)
Ela era filha de Etal Anbuail, um rei Feérico dos Tuatha Dé Danann "povos da deusa Danu"; uma filidh - um nome que mais tarde foi atribuido aos poetas da Irlanda com proezas proféticas, uma vez que Ibormeith era a deusa das profecias, de certa forma semelhante a um "bardo", como se diz em Português. A cada Samhain, 31 de Outubro, quando o Mundo dos Vivos se aproximava do Mundo dos Mortos, ela transformava-se num cisne, até ao Samhain seguinte em que regressava à sua forma humana. Numa das versões desse conto, Ibormeith, após consulta ou por iniciativa própria, apaixona-se por Óengus. Numa noite, ela aparece nos sonhos dele tocando a mais bela melodia e quando ele acorda sabe que está apaixonado mas não sabia quem era aquela bela mulher nem onde a poderia encontrar. Ele fica completamente down bad e cada dia que passa só pensa em voltar sonhar com ela outra vez, e ela todas as noites volta a aparecer-lhe no Mundos dos Sonhos. Um dia, Óengus perde o apetite e adoece. Um médico foi chamado. Ele adivinhou a causa da doença de Óengus e disse a Bóann, mãe de Óengus, para encontrar a jovem dos sonhos dele. Bóann procurou durante um ano, mas sem sucesso. Então, eles pediram ajuda ao seu pai, o Dagdha, que também procurou um ano mas sem sucesso. Então foi pedido ao seu irmão Bodb que encontrasse um lugar com a descrição segundo os sonhos. Mas o pai dela, Etal, não permitia que qualquer um ficasse com a mão da sua filha e então revelou que para a conquistar teria que esperar pelo Loch Bél Dragain que significa "Lago da Boca do Dragão" para a encontrar na manhã do Samhain e a chamasse pelo nome. Nesse dia havia 150 cisnes* nesse lago, carregando correntes de prata e Óengus começou a panicar por não encontrar a sua Ibormeith, mas foi então que reparou num cisne mais bonito que os outros, com correntes de ouro e prata, e quando disse o seu nome ela revelou a sua forma humana e perguntou-lhe porque demorou tanto tempo.
Depois disse transformaram-se em cisnes e cantaram uma música tão bela que os humanos dormiram durante 3 dias e Óengus ficou conhecido como deus do amor e da juventude.
*Na mitologia irlandesa, o número 150 refere-se frequentemente aos Cinquenta Guerreiros dos Tuatha Dé Danann e a figura dos cisnes é frequente e também utilizada nas obras de Hans Christian Andersen e Tchaikovsky. Outras versões do conto não dizem cisnes, dizem aves, ou a história acontece de maneira ligeiramente diferente - quem conta um conto acrescenta um ponto.![image]
-
 @ ba3b4b1d:eadff0d3
2025-05-09 23:40:27
@ ba3b4b1d:eadff0d3
2025-05-09 23:40:27
O culto de Sol Invictus (Sol Invicto, ou "Sol Não Vencido") foi oficialmente instituído como religião estatal do Império Romano pelo imperador Aureliano em 274 d.C., marcando um momento relevante na história religiosa romana. Este culto, que celebrava o Sol como divindade suprema e invencível, estabeleceu celebrações anuais a 25 de Dezembro, uma data estrategicamente escolhida pela sua proximidade com o solstício de Inverno no calendário juliano. Contudo, o culto de Sol Invictus não surgiu isoladamente; tratava-se, na verdade, de uma reformulação e revitalização de práticas religiosas romanas muito mais antigas que veneravam Sol, a personificação deificada do Sol, uma figura presente na religião romana desde os tempos da República.
Antes da oficialização por Aureliano, o culto ao Sol já era praticado em Roma sob diversas formas. Na mitologia romana, Sol era frequentemente associado a deuses solares de outras culturas, como o grego Hélios e, mais tarde, o persa Mitra, cujo culto (o mitraísmo) alcançou grande popularidade entre os soldados romanos nos séculos II e III d.C. O mitraísmo, com os seus rituais iniciáticos e ênfase no Sol como símbolo de renovação e vitória, influenciou profundamente a iconografia e os conceitos do culto de Sol Invictus. A decisão de Aureliano de promover Sol Invictus como divindade unificadora do Império não foi apenas religiosa, mas também política: numa era de crises internas e externas, o culto ao Sol servia como símbolo de estabilidade, poder e unidade, sobretudo após a vitória de Aureliano contra a rainha Zenóbia do Reino de Palmira, cuja derrota foi atribuída à protecção divina do Sol.
Um dos festivais mais significativos associados ao culto era o Dies Natalis Solis Invicti ("Aniversário do Sol Invicto"), celebrado no solstício de Inverno, por volta de 21 de Dezembro, quando o dia começava a prolongar-se novamente, simbolizando a vitória do Sol sobre a escuridão. Este festival, profundamente enraizado no ciclo natural e astronómico, celebrava o renascimento do Sol e a sua força invencível. A proximidade temporal entre o Dies Natalis e a data de 25 de Dezembro, oficialmente adoptada para Sol Invictus, facilitou a sobreposição de significados e práticas religiosas. A ascensão do Cristianismo no Império Romano, particularmente após a conversão do imperador Constantino no início do século IV, conduziu a uma complexa interacção entre os cultos pagãos e a nova religião. É amplamente reconhecido pelos historiadores que o Cristianismo, ao estabelecer-se como religião dominante, absorveu e adaptou elementos de festivais pagãos para facilitar a conversão das populações e consolidar a sua influência. A escolha do 25 de Dezembro como data do nascimento de Jesus Cristo, que não tem fundamento nos textos bíblicos canónicos, é um exemplo evidente deste sincretismo. A data coincidia convenientemente com as celebrações de Sol Invictus e outros festivais pagãos, como a Saturnália, um período de festividades em honra do deus Saturno que ocorria em meados de Dezembro. O simbolismo do Sol, associado à luz, renovação e vitória sobre as trevas, era facilmente adaptável à narrativa cristã. Jesus, frequentemente descrito como a "Luz do Mundo" nos evangelhos (João 8:12), foi associado ao simbolismo solar, e a sua ressurreição passou a ser celebrada como uma vitória sobre a morte, semelhante ao retorno triunfal do Sol no solstício. A iconografia cristã também reflectiu esta influência: imagens de Cristo com uma auréola, reminiscentes dos raios solares, ecoavam representações de Sol Invictus e Hélios. Além disso, o mitraísmo, com os seus rituais de renovação e ênfase num salvador divino, apresentava paralelos com o Cristianismo, o que poderá ter facilitado a transição de fiéis de um culto para o outro.
Importa notar que a adopção do 25 de Dezembro como o Natal cristão não foi imediata. Registos históricos sugerem que a data só foi formalmente estabelecida no século IV, durante o reinado de Constantino e sob a influência da Igreja de Roma. O Papa Júlio I, por volta de 350 d.C., é frequentemente creditado por oficializar a celebração do nascimento de Cristo nesta data. Esta escolha foi estratégica, pois permitiu que o Cristianismo se sobrepusesse aos festivais pagãos, reinterpretando as suas tradições num contexto cristão. Paralelamente, na Sibéria, os cultos xamânicos envolvendo o cogumelo Amanita muscaria também se relacionam com o solstício de Inverno. Povos como os Evenki e os Chukchi utilizavam este cogumelo alucinogénio em rituais para enfrentar o rigoroso Inverno, induzindo visões de renas voadoras e trenós, que alguns estudiosos associam à origem das lendas do Pai Natal. A Amanita muscaria, com o seu píleo vermelho e branco, crescia sob pinheiros, que se tornaram símbolos das árvores de Natal. Os xamãs siberianos distribuíam estes cogumelos secos como "presentes" durante o solstício, muitas vezes entrando nas casas pela chaminé devido à neve, um costume que ecoa na figura do Pai Natal. Assim, tanto o culto de Sol Invictus como os rituais siberianos da Amanita muscaria convergem no simbolismo do solstício de Inverno, influenciando, de formas distintas, as tradições natalícias cristãs.
A escolha de 25 de Dezembro facilitou a integração de tradições pagãs, como a Saturnália e os cultos solares, numa narrativa cristã, com Jesus como a "Luz do Mundo".
Assim, o culto de Sol Invictus e as suas raízes no culto romano a Sol desempenharam um papel crucial na formação das celebrações cristãs do Natal. A amalgamação de elementos pagãos e cristãos reflecte a capacidade do Cristianismo de se adaptar às culturas locais, transformando símbolos e rituais profundamente enraizados em novas expressões de fé. Este processo de sincretismo não só garantiu a sobrevivência do Cristianismo num mundo religiosamente diverso, como também moldou a forma como o Natal é celebrado até hoje, com ecos das antigas tradições solares ainda presentes na sua simbologia de luz e renovação.
-
 @ 6be5cc06:5259daf0
2025-04-28 01:05:49
@ 6be5cc06:5259daf0
2025-04-28 01:05:49Eu reconheço que Deus, e somente Deus, é o soberano legítimo sobre todas as coisas. Nenhum homem, nenhuma instituição, nenhum parlamento tem autoridade para usurpar aquilo que pertence ao Rei dos reis. O Estado moderno, com sua pretensão totalizante, é uma farsa blasfema diante do trono de Cristo. Não aceito outro senhor.
A Lei que me guia não é a ditada por burocratas, mas a gravada por Deus na própria natureza humana. A razão, quando iluminada pela fé, é suficiente para discernir o que é justo. Rejeito as leis arbitrárias que pretendem legitimar o roubo, o assassinato ou a escravidão em nome da ordem. A justiça não nasce do decreto, mas da verdade.
Acredito firmemente na propriedade privada como extensão da própria pessoa. Aquilo que é fruto do meu trabalho, da minha criatividade, da minha dedicação, dos dons a mim concedidos por Deus, pertence a mim por direito natural. Ninguém pode legitimamente tomar o que é meu sem meu consentimento. Todo imposto é uma agressão; toda expropriação, um roubo. Defendo a liberdade econômica não por idolatria ao mercado, mas porque a liberdade é condição necessária para a virtude.
Assumo o Princípio da Não Agressão como o mínimo ético que devo respeitar. Não iniciarei o uso da força contra ninguém, nem contra sua propriedade. Exijo o mesmo de todos. Mas sei que isso não basta. O PNA delimita o que não devo fazer — ele não me ensina o que devo ser. A liberdade exterior só é boa se houver liberdade interior. O mercado pode ser livre, mas se a alma estiver escravizada pelo vício, o colapso será inevitável.
Por isso, não me basta a ética negativa. Creio que uma sociedade justa precisa de valores positivos: honra, responsabilidade, compaixão, respeito, fidelidade à verdade. Sem isso, mesmo uma sociedade que respeite formalmente os direitos individuais apodrecerá por dentro. Um povo que ama o lucro, mas despreza a verdade, que celebra a liberdade mas esquece a justiça, está se preparando para ser dominado. Trocará um déspota visível por mil tiranias invisíveis — o hedonismo, o consumismo, a mentira, o medo.
Não aceito a falsa caridade feita com o dinheiro tomado à força. A verdadeira generosidade nasce do coração livre, não da coerção institucional. Obrigar alguém a ajudar o próximo destrói tanto a liberdade quanto a virtude. Só há mérito onde há escolha. A caridade que nasce do amor é redentora; a que nasce do fisco é propaganda.
O Estado moderno é um ídolo. Ele promete segurança, mas entrega servidão. Promete justiça, mas entrega privilégios. Disfarça a opressão com linguagem técnica, legal e democrática. Mas por trás de suas máscaras, vejo apenas a velha serpente. Um parasita que se alimenta do trabalho alheio e manipula consciências para se perpetuar.
Resistir não é apenas um direito, é um dever. Obedecer a Deus antes que aos homens — essa é a minha regra. O poder se volta contra a verdade, mas minha lealdade pertence a quem criou o céu e a terra. A tirania não se combate com outro tirano, mas com a desobediência firme e pacífica dos que amam a justiça.
Não acredito em utopias. Desejo uma ordem natural, orgânica, enraizada no voluntarismo. Uma sociedade que se construa de baixo para cima: a partir da família, da comunidade local, da tradição e da fé. Não quero uma máquina que planeje a vida alheia, mas um tecido de relações voluntárias onde a liberdade floresça à sombra da cruz.
Desejo, sim, o reinado social de Cristo. Não por imposição, mas por convicção. Que Ele reine nos corações, nas famílias, nas ruas e nos contratos. Que a fé guie a razão e a razão ilumine a vida. Que a liberdade seja meio para a santidade — não um fim em si. E que, livres do jugo do Leviatã, sejamos servos apenas do Senhor.
-
 @ c1e9ab3a:9cb56b43
2025-05-09 23:10:14
@ c1e9ab3a:9cb56b43
2025-05-09 23:10:14I. Historical Foundations of U.S. Monetary Architecture
The early monetary system of the United States was built atop inherited commodity money conventions from Europe’s maritime economies. Silver and gold coins—primarily Spanish pieces of eight, Dutch guilders, and other foreign specie—formed the basis of colonial commerce. These units were already integrated into international trade and piracy networks and functioned with natural compatibility across England, France, Spain, and Denmark. Lacking a centralized mint or formal currency, the U.S. adopted these forms de facto.
As security risks and the practical constraints of physical coinage mounted, banks emerged to warehouse specie and issue redeemable certificates. These certificates evolved into fiduciary media—claims on specie not actually in hand. Banks observed over time that substantial portions of reserves remained unclaimed for years. This enabled fractional reserve banking: issuing more claims than reserves held, so long as redemption demand stayed low. The practice was inherently unstable, prone to panics and bank runs, prompting eventual centralization through the formation of the Federal Reserve in 1913.
Following the Civil War and unstable reinstatements of gold convertibility, the U.S. sought global monetary stability. After World War II, the Bretton Woods system formalized the U.S. dollar as the global reserve currency. The dollar was nominally backed by gold, but most international dollars were held offshore and recycled into U.S. Treasuries. The Nixon Shock of 1971 eliminated the gold peg, converting the dollar into pure fiat. Yet offshore dollar demand remained, sustained by oil trade mandates and the unique role of Treasuries as global reserve assets.
II. The Structure of Fiduciary Media and Treasury Demand
Under this system, foreign trade surpluses with the U.S. generate excess dollars. These surplus dollars are parked in U.S. Treasuries, thereby recycling trade imbalances into U.S. fiscal liquidity. While technically loans to the U.S. government, these purchases act like interest-only transfers—governments receive yield, and the U.S. receives spendable liquidity without principal repayment due in the short term. Debt is perpetually rolled over, rarely extinguished.
This creates an illusion of global subsidy: U.S. deficits are financed via foreign capital inflows that, in practice, function more like financial tribute systems than conventional debt markets. The underlying asset—U.S. Treasury debt—functions as the base reserve asset of the dollar system, replacing gold in post-Bretton Woods monetary logic.
III. Emergence of Tether and the Parastatal Dollar
Tether (USDT), as a private issuer of dollar-denominated tokens, mimics key central bank behaviors while operating outside the regulatory perimeter. It mints tokens allegedly backed 1:1 by U.S. dollars or dollar-denominated securities (mostly Treasuries). These tokens circulate globally, often in jurisdictions with limited banking access, and increasingly serve as synthetic dollar substitutes.
If USDT gains dominance as the preferred medium of exchange—due to technological advantages, speed, programmability, or access—it displaces Federal Reserve Notes (FRNs) not through devaluation, but through functional obsolescence. Gresham’s Law inverts: good money (more liquid, programmable, globally transferable USDT) displaces bad (FRNs) even if both maintain a nominal 1:1 parity.
Over time, this preference translates to a systemic demand shift. Actors increasingly use Tether instead of FRNs, especially in global commerce, digital marketplaces, or decentralized finance. Tether tokens effectively become shadow base money.
IV. Interaction with Commercial Banking and Redemption Mechanics
Under traditional fractional reserve systems, commercial banks issue loans denominated in U.S. dollars, expanding the money supply. When borrowers repay loans, this destroys the created dollars and contracts monetary elasticity. If borrowers repay in USDT instead of FRNs:
- Banks receive a non-Fed liability (USDT).
- USDT is not recognized as reserve-eligible within the Federal Reserve System.
- Banks must either redeem USDT for FRNs, or demand par-value conversion from Tether to settle reserve requirements and balance their books.
This places redemption pressure on Tether and threatens its 1:1 peg under stress. If redemption latency, friction, or cost arises, USDT’s equivalence to FRNs is compromised. Conversely, if banks are permitted or compelled to hold USDT as reserve or regulatory capital, Tether becomes a de facto reserve issuer.
In this scenario, banks may begin demanding loans in USDT, mirroring borrower behavior. For this to occur sustainably, banks must secure Tether liquidity. This creates two options: - Purchase USDT from Tether or on the secondary market, collateralized by existing fiat. - Borrow USDT directly from Tether, using bank-issued debt as collateral.
The latter mirrors Federal Reserve discount window operations. Tether becomes a lender of first resort, providing monetary elasticity to the banking system by creating new tokens against promissory assets—exactly how central banks function.
V. Structural Consequences: Parallel Central Banking
If Tether begins lending to commercial banks, issuing tokens backed by bank notes or collateralized debt obligations: - Tether controls the expansion of broad money through credit issuance. - Its balance sheet mimics a central bank, with Treasuries and bank debt as assets and tokens as liabilities. - It intermediates between sovereign debt and global liquidity demand, replacing the Federal Reserve’s open market operations with its own issuance-redemption cycles.
Simultaneously, if Tether purchases U.S. Treasuries with FRNs received through token issuance, it: - Supplies the Treasury with new liquidity (via bond purchases). - Collects yield on government debt. - Issues a parallel form of U.S. dollars that never require redemption—an interest-only loan to the U.S. government from a non-sovereign entity.
In this context, Tether performs monetary functions of both a central bank and a sovereign wealth fund, without political accountability or regulatory transparency.
VI. Endgame: Institutional Inversion and Fed Redundancy
This paradigm represents an institutional inversion:
- The Federal Reserve becomes a legacy issuer.
- Tether becomes the operational base money provider in both retail and interbank contexts.
- Treasuries remain the foundational reserve asset, but access to them is mediated by a private intermediary.
- The dollar persists, but its issuer changes. The State becomes a fiscal agent of a decentralized financial ecosystem, not its monetary sovereign.
Unless the Federal Reserve reasserts control—either by absorbing Tether, outlawing its instruments, or integrating its tokens into the reserve framework—it risks becoming irrelevant in the daily function of money.
Tether, in this configuration, is no longer a derivative of the dollar—it is the dollar, just one level removed from sovereign control. The future of monetary sovereignty under such a regime is post-national and platform-mediated.
-
 @ 57d1a264:69f1fee1
2025-05-06 05:49:01
@ 57d1a264:69f1fee1
2025-05-06 05:49:01I don’t like garlic. It’s not a dislike for the taste in the moment, so much as an extreme dislike for the way it stays with you—sometimes for days—after a particularly garlicky meal.
Interestingly enough, both of my brothers love garlic. They roast it by itself and keep it at the ready so they can have a very strong garlic profile in their cooking. When I prepare a dish, I don’t even see garlic on the ingredient list. I’ve cut it out of my life so completely that my brain genuinely skips over it in recipes. While my brothers are looking for ways to sneak garlic into everything they make, I’m subconsciously avoiding it altogether.
A few years back, when I was digging intensely into how design systems mature, I stumbled on the concept of a design system origin story. There are two extreme origin stories and an infinite number of possibilities between. On one hand you have the grassroots system, where individuals working on digital products are simply trying to solve their own daily problems. They’re frustrated with having to go cut and paste elements from past designs or with recreating the same layouts over and over, so they start to work more systematically. On the other hand, you have the top down system, where leadership is directing teams to take a more systematic approach, often forming a small partially dedicated core team to tackle some centralized assets and guidelines for all to follow. The influences in those early days bias a design system in interesting and impactful ways.
We’ve established that there are a few types of bias that are either intentionally or unintentionally embedded into our design systems. Acknowledging this is a great first step. But, what’s the impact of this? Does it matter?
I believe there are a few impacts design system biases, but there’s one that stands out. The bias in your design system makes some individuals feel the system is meant for them and others feel it’s not. This is a problem because, a design system cannot live up to it’s expected value until it is broadly in use. If individuals feel your design system is not for them, the won’t use it. And, as you know, it doesn’t matter how good your design system is if nobody is using it.
originally posted at https://stacker.news/items/972641
-
 @ 30611079:ecac89f8
2025-05-10 13:30:51
@ 30611079:ecac89f8
2025-05-10 13:30:51Um Shell Script simples para facilitar backups bip39 baseados nos números das palavras, coloque o script na mesma pasta que o arquivo contendo as palavras, passe o idioma no 1º argumento (Ex. english) e as palavras em sequência, a saída serão os números correspondentes as palavras passadas no idioma selecionado
```
!/bin/bash
Enter in correct diretory
if [ ${0%/} == $0 ]; then cd ${PWD} elif [ -e ${PWD}/${0%/} ]; then cd ${PWD}/${0%/} else cd ${0%/} fi
file="$1.txt"
index=0 numbers=() for word in "$@"; do while IFS= read -r linha; do if [[ "$linha" == "$word" ]]; then numbers+=($index) break fi ((index++)) done < "$file" index=0 done echo "${numbers[@]}" ```
Fiz para aprender um pouco de Shell Script, podem dizer se está bom e se dá para melhorar algo?
Também fiz outro que faz o processo reverso
-
 @ 078d6670:56049f0c
2025-05-09 13:22:26
@ 078d6670:56049f0c
2025-05-09 13:22:26It was a dark and stormy night. It had to be: Weather had been fired. If they were working for him he would have fired them, but that is just embarrassed arrogance talking. He remembers standing in the middle of his office, his trashed office. It looked like a hurricane had hit it, or vagrants had been living in it for years, nothing of value was left intact. Monitors were shattered on the floor, couches were covered in debris. There was evidence of food and magazine pages in every gaze space. His supervisor, his name escaped him, was grey with anger. “Explain this!” he had shouted with a tremble, but he couldn’t. Every time he tried to think of the events of the day he met a dazzling white blankness.
He was escorted, handcuffed, to a room by two security guards with his supervisor trailing them. Weather felt humiliated and frustrated, but he didn’t know why. He sat, shivering slightly, in a low-lit conference room he had never seen before. Actually, he doesn’t remember any windows or any specific light source, just a haze of shadows. The big boss is sitting opposite him, looking haggard and white as a sun-bleached shell. His supervisor was sitting on his right looking equally haggard and even depressed. They appeared genuine and he knew it was bad news for him.
“You’ve embarrassed this company! There is even a chance you have ruined us all and you have the audacity to sit there and pretend that you can’t remember a thing!”
He knew there was no point in arguing, he had no ideas with which to make up any argument. He sat staring into space.
“At least, give us a story. Tell us how bored you were and tried to create your own weather system by running around the room swinging the fan around like a sugar mad teenager!”
He couldn’t even clear his throat. He couldn’t lift his eyes to meet theirs. He knew his career was over and they were fearful all their ideals had crashed irreparably. He stared into space at the globe standing in the middle of the table. The more he stared at it the more he realized that it seemed to have an atmosphere around it. There were clouds covering patches of the earth. He didn’t dare bring their attention to it. The only memories he could dredge up seemed like dreams, and they’re hardly constitute a defence.
He looked up at their faces finally, surprised to see more alarm than anger, like they were actually afraid of him. They both stood up suddenly, wanting to get out the room as quickly as possible.
“You have brought Global Sky Incorporated into disrepute. You’ve embarrassed us. You have possibly ruined hundreds of careers here! We never want to see you again! You are never to come within a hundred metres of this building. You can never use your research ever again, it never happened. Everything you have ever written will be classified and restricted until you are dead!” The big boss was shaking wild, Weather was grateful for the security guards that hurled him out of his chair and marched him out of the building.
The afternoon sky had been a deathly grey. It had occurred to him but now he was a little shocked at how much control they had over the weather, maybe it was a good thing that he had been fired, but probably a bad thing as they would certainly make worse mistakes than him, whatever he might have done. He was confused, not sure if he been fired for trashing his office or for state of the weather. About the weird weather he has no idea, all he can remember is a dazzling blank whiteness, and that is hardly a memory.
He couldn’t face going directly home, jumped on public transport travelling on tracks laid down on old unused highways and headed for the city beach, or what passed for a beach. He sat on a concrete bench gazing across the grey sand at the shimmering waves. They weren’t shimmering because of the sparkling sunlight, but the contaminates in the water. But still it was tranquil enough. He tried to think about his day, but couldn’t get past the white blankness, everything else before that was like a postcard from someone else’s holiday, and they looked like movies he might have seen. He has a framed vision of himself in his office with office supplies flying around him without touching him. Clearly, as they weren’t touching him, it had nothing to do with his behaviour. He is a victim here. It wasn’t his fault, the world was changing and the powers that be wanted more control. It seems like Global Weather Incorporated (GWI) lost control of their equipment and need a fall guy, they didn’t need him anymore. Squeezed his brain for the algorithms, then threw him onto the streets. He was nothing without his research, it’s all he had done his entire life. He would have to pursue it, but that would as useful as talking to a brick wall, the world was less transparent; government, science and advertising companies had a law of their own and a police force to uphold them.
He believed in good and the unveiling of truth. He had a romantic connection to the idea that truth grew in people’s hearts that everyone wanted the best for everyone else, no matter what skin colour, car colour they had, or star sign they were born under. Everybody wanted peace, a roof over their heads and food in their bellies; and wanted these things for their neighbours too. If only his neighbours had the same beliefs.
It was late afternoon now. He could tell by the slight luminosity of the grey clouds near the horizon, close to a cloudless gap, a slit above the horizon through which the sun could bid its final farewell to the day. He was in no mood for a sunset minute. He picked his bum off the bench, dusted it off and began his journey home, not wanting to be left in the dark in the city, opportune prey for corrupt cops. Everyone was coming out of the offices, beginning the big commute home. Car pools had reshaped their cars to fit more people in, and many climbed on to the reinvented trams, sitting if they were lucky, holding onto ceiling straps if they were unlucky like him. Couples sat together staring into each other’s eyes, friends joked and discussed their office politics. He hated the commute back and forth from work, it made him feel alone, desperate and unwanted. There had been no office politics for him, it was just him and his mostly silent supervisor.
The sky was struck red, a wound inflicted on the sky, it bleed for a minute then all went dark. Reality shuddered as it returned to him, this would be his last commute along this route. He was without a job; his recently regained self-esteem was destroyed. At the end of university he had wondered if he had a career anywhere, if his self-inflicted social isolation had been worth it and GWI had lifted him out of academic gutter and placed him on a pedestal. And now he was turfed out like a partly cloudy day from a child’s memory, flicked off like an ant off a picnic blanket.
Litter was being chased up and down the aisle, wrapping around legs and trying to hide from the wind amongst commuters’ bags. He didn’t notice that the commuters were becoming concerned about the weather, heads turned to look outside where the clouds were blacker than night. Wind has beating on windows, knocking on doors trying to escape from itself. Loose objects were starting to drift.
“Puck, I’m so stupid!” Weather lamented aloud as a flash of lightning brightened the dusk for a second. He should have protected his research, patented it in his own name. Stupidly, he had thought he would be with GWI for the rest of his life. He had given his life over to GWI and they had thrown it away for an office in disarray. It might have looked like an unnatural disaster, but they could have at least let him evaluate their equipment to check for systems failure. Why he hadn’t opened his mouth and flung accusations back at them? Probably because they had looked angrier than he could possibly have gotten faced with a memory of shimmering blankness.
The weather was surreal, he casually noted it as something GWI would have to correct, something existing outside his present unemployed reality, their problem. His cellphone’s classic “Thunderstuck” ringtone charged the air.
“What’s happening with the weather, dude? I thought I read in the paper that it was supposed to be sunny skies and calm seas. I wanted to go for an evening dive at Devil’s.”
“I’ve no idea, I’ve been fired,” he managed to say calmly before he hung up.
“It’s not my responsibility,” he thought to himself and promptly switched his phone off. He had given his private cellphone number to a few select acquaintances he had tried to impress when he had just got his ‘prestigious’ job. He thought he might finally be able to get his social life out of his house by sharing information with people he had met in supermarkets, recognizing their faces from university. They were jocks obsessed about the weather for their hedonistic lifestyles and they had never invited him out, only phoning to find out about the weather.
He jumped off at his usual stop and leaned into the wind watching his feet moving past one another, his mind seething at the injustice of not having a fair trial where they showed him evidence of him been directly involved in the trashing of his office. He could only remember standing in the middle of it and his office revolving around him, but that was only a flash, there is nothing before that except the facts. Him working on algorithms of weather activation, them tinkering with the clouds. They were practically at the end of their testing, their final live weather event before taking on the whole world’s weather, he knows that, but everyday was still just the same as every other day, him at the computer, them throwing lightning bolts. “Puck! I should’ve challenged them,” he shouted into the howling wind at GSI with all the frustration of his past mistakes. But his voice was lost into the atmosphere.
-
 @ b8851a06:9b120ba1
2025-05-09 22:54:43
@ b8851a06:9b120ba1
2025-05-09 22:54:43The global financial system is creaking under its own weight. The IMF is urging banks to shore up capital, cut risk, and brace for impact. Basel III is their answer, a last-ditch effort to reinforce a brittle foundation.
But behind the scenes, a quieter revolution is under way.
Bitcoin, the world’s first stateless digital asset, is no longer on the sidelines. It’s entering the Basel conversation: not by invitation, but by inevitability.
Basel III: The System’s Self-Diagnosis
Basel III is more than a technical rulebook. It’s a confession: an admission that the global banking system is vulnerable. Created in the aftermath of 2008, it calls for: • Stronger capital reserves: So banks can survive losses. • Lower leverage: To reduce the domino effect of overexposure. • Liquidity buffers: To weather short-term shocks without collapsing.
But here’s the kicker: these rules are hostile to anything outside the fiat system. Bitcoin gets hit with a punitive 1,250% risk weight. That means for every $1 of exposure, banks must hold $1 in capital. The message from regulators? “You can hold Bitcoin, but you’ll pay for it.”
Yet that fear: based framing misses a bigger truth: Bitcoin doesn’t just survive in this environment. It thrives in it.
Bitcoin: A Parallel System, Built on Hard Rules
Where Basel III imposes “fiat discipline” from the top down, Bitcoin enforces it from the bottom up: with code, math, and transparency.
Bitcoin is not just a hedge. It’s a structural antidote to systemic fragility.
Volatility: A Strategic Asset
Yes, Bitcoin is volatile. But in a system that devalues fiat on a schedule, volatility is simply the cost of freedom. Under Basel III, banks are expected to build capital buffers during economic expansions.
What asset allows you to build those buffers faster than Bitcoin in a bull market?
When the cycle turns, those reserves act as shock absorbers: converting volatility into resilience. It’s anti-fragility in motion.
Liquidity: Real, Deep, and Global
Bitcoin settled over $19 trillion in transactions in 2024. That’s not hypothetical liquidity. it’s real, measurable flow. Unlike traditional high-quality liquid assets (HQLAs), Bitcoin is: • Available 24/7 • Borderless • Not dependent on central banks
By traditional definitions, Bitcoin is rapidly qualifying for HQLA status. Even if regulators aren’t ready to admit it.
Diversification: Breaking the Fiat Dependency
Basel III is designed to pull banks back into the fiat matrix. But Bitcoin offers an escape hatch. Strategic Bitcoin reserves are not about speculation, they’re insurance. For family offices, institutions, and sovereign funds, Bitcoin is the lifeboat when the fiat ship starts taking on water.
Regulatory Realignment: The System Reacts
The Basel Committee’s new rules on crypto exposures went live in January 2025. Around the world, regulators are scrambling to define their stance. Every new restriction placed on Bitcoin only strengthens its legitimacy, as more institutions ask: Why so much resistance, if it’s not a threat?
Bitcoin doesn’t need permission. It’s already being adopted by over 150 public companies, forward-looking states, and a new class of self-sovereign individuals.
Conclusion: The Real Question
This isn’t just about Bitcoin fitting into Basel III.
The real question is: How long can Basel III remain relevant in a world where Bitcoin exists?
Bitcoin is not the risk. It’s the reality check. And it might just be the strongest capital buffer the system has ever seen.
Gradually then suddenly.
-
 @ 866e0139:6a9334e5
2025-05-10 11:29:23
@ 866e0139:6a9334e5
2025-05-10 11:29:23\ Autor: Kerstin Chavent. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Wir halten uns für erwacht, weil wir das Coronanarrativ durchschaut haben, regierungskritisch unterwegs sind und Russland nicht für den ärgsten Feind der Demokratie halten? Wir informieren uns in alternativen und unabhängigen Medien, folgen geistigen Führern und sehen Spiritualität als einen Teil unseres Daseins auf der Erde? Vielleicht sind wir mit Meditationstechniken vertraut, machen Yoga oder nehmen bewusstseinserweiternde Substanzen zu uns? Wir denken, andere würden noch schlafen, weil sie das nicht tun? Dann haben wir noch einen weiten Weg vor uns.
Aufwachen — wir tun es jeden Morgen und oft auch während der Nacht. Der Kopf ist schwer, vielleicht ein wenig verwirrt, wie in einem Nebel. Die Schleier der Träume hängen noch an uns. Wir sind noch nicht ganz da und brauchen eine Dusche, einen Kaffee oder frische Luft, um langsam durchzukommen und den Tag zu beginnen. In den seltensten Fällen ist es so, dass wir die Augen aufschlagen und hellwach sind, vollkommen präsent und klar. So passt die Metapher auf das, was heute auf den Bewusstseinszustand der Menschen angewendet wird.
Was bedeutet es, wach zu sein? Ein waches Bewusstsein zu haben? Was ist Bewusstsein? Eine der großen Referenzen für Psychologie und Pädagogik hat einen eher beschränkten und materialistisch orientierten Bewusstseinsbegriff. Demnach reiche Bewusstsein nicht über das normale Denken hinaus. Bewusstsein habe ein Mensch immer dann, wenn er in der Lage ist, zu bedenken, ob das, was er tut, vernünftig ist. Das Bewusstsein sei an das Gehirn gebunden. Ein Bewusstsein ohne Aktivität von Nervenzellen im menschlichen Gehirn gebe es nicht. Das sei wissenschaftlicher Konsens. Über noch etwas ist man sich einig:
Nach Jahrhunderten der Bemühung von Neurowissenschaftlern, Psychologen und Philosophen bleibt zu der Frage, wie das Gehirn uns denn Bewusstsein verleiht, wie es Empfindungen, Gefühle und Subjektivität entstehen lässt, nur eine Gewissheit: Wir haben keine Ahnung (1).
Mehr Ahnung haben wir, wenn es darum geht, das menschliche Bewusstsein zu manipulieren. Voraussetzung ist, die zu manipulierende Person in Unkenntnis zu lassen. Es wird ein Gefühl von Machtlosigkeit in ihr erzeugt und ein System von Belohnung und Strafe aufgebaut, um eine autoritäre Machtstruktur, die kein Feedback und keine Änderung ohne Zustimmung oder Anordnung der Führung zulässt, zu installieren. Hierfür ist keine Gewaltanwendung erforderlich. Für eine mentale Umprogrammierung reicht es, jede Form von Kritik zu unterdrücken und Kritiker zu diffamieren, indem man ihnen persönliche Rachemotive oder menschliche Schwäche andichtet (2).
Manipulation mit Angst
Angst ist eines der wirksamsten Mittel, um das Bewusstsein der Menschen zu manipulieren. Wer Angst hat, lässt sich leicht täuschen. Das Bewusstsein verengt sich regelrecht. Damit ergibt sich ein nahezu unerschöpflicher Fundus von Methoden zur Bewusstseinskontrolle. Welche, das erleben wir täglich: die Erschaffung einer Unterhaltungsindustrie und die Verbreitung von Filmen, in denen es vor allem um Mord, Verrat, Krankheit und Betrug geht; Medien, die maximale Verwirrung schaffen; giftige Substanzen in Nahrungsmitteln und Wasser; ein knechtendes Finanzsystem; Medikamente, von denen wir möglichst früh und möglichst lange abhängig sind.
Wer das Bewusstsein der Menschen und damit die Welt in den Griff bekommen will, fängt früh an. Er erfindet zum Beispiel Religionen, die sich nach Möglichkeit gegenseitig bekämpfen.
Er erzählt Geschichten, in denen die eine Hälfte der Menschheit der anderen per se unterlegen sein soll, erfindet Götter, die die einen privilegieren und die anderen bestrafen, und ein Paradies, das irgendwoanders ist als dort, wo wir gerade sind.
Alles ist darauf ausgerichtet, dass der Mensch sich klein, unwürdig, schuldig und vor allem ohnmächtig fühlt. Auf keinen Fall darf er sich seiner angeborenen Möglichkeiten bewusstwerden! Hierfür werden Kinder so früh wie möglich von den Eltern getrennt, bekommen in staatlichen Schulen ihre Kreativität und Eigenmacht aberzogen, werden von technischen Geräten abhängig gemacht und durch Geschlechterverwirrung davon abgehalten, ihre Identität zu entwickeln. So werden sie darauf vorbereitet, zu guten Soldaten des Systems zu werden und in jeden Krieg zu ziehen, der ihnen als notwendig verkauft wird.
Project Blue Beam
Immer mehr Menschen wissen das. Immer mehr erkennen, was auf der Bühne des Welttheaters gespielt wird. Doch sind wir deshalb erwacht? Reicht es, alternative Medien zu konsumieren, bewusstseinserweiternde Substanzen zu sich zu nehmen und regelmäßig zu meditieren, um das eigene Bewusstsein zu entwickeln? Reichen die Bücher, die Workshops und die charismatischen Führer, die überall zu finden sind? Sind wir erwacht, nur weil der Nachbar noch schläft?
Wie würden wir zum Beispiel reagieren, wenn das Projekt „Blue Beam“ durchgespielt werden würde? Natürlich soll es sich hierbei um eine Verschwörungstheorie handeln. Aber nur mal angenommen. Es geht darum, durch das Erschaffen einer allgemeinen Unsicherheit und Hysterie eine neue Weltordnung durchzusetzen.
In einer ersten Etappe sollen künstlich erschaffene Naturkatastrophen dafür sorgen, dass die Menschen sämtliche religiöse Fundamente in Frage stellen. In einer zweiten Etappe werden mittels dreidimensionaler Hologramme verschiedene Gottesbilder in den Himmel projiziert mit dem Ziel, eine Einheitsreligion zu proklamieren. In einer dritten Etappe sollen mittels Niederfrequenzen und per Satellit Gedankengänge gezielt beeinflusst werden, und in einem letzten Schritt soll die Menschheit davon überzeugt werden, dass in allen großen Städten der Welt eine Invasion Außerirdischer nahe bevorsteht.
Jede große Nation soll dazu aufgefordert werden, ihr nukleares Potenzial als Abwehr zu benutzen. Es soll sich jedoch um ein Fake-Manöver handeln. Den Nationen, nun ihrer Waffen entledigt, bliebe nur noch die Hoffnung auf einen göttlichen Eingriff. Alle „erwachten“ Menschen würden von „guten“ außerirdischen Kräften „gerettet“ und entführt werden — womit der neuen Weltordnung auf Erden nichts mehr im Wege stünde. Der Rest der Menschheit würde mittels über elektronische Geräte verbreiteter böser Geister in den Wahnsinn und die totale Hoffnungslosigkeit getrieben werden.
Selbstwirksamkeit?
Die Geschichte ist haarsträubend. Doch wer könnte beschwören, dass sie technisch nicht möglich wäre? Wer könnte sich sicher sein, einer False-Flag-Aktion nicht auf den Leim zu gehen? Wer könnte von sich behaupten, so erwacht, so in seinem Bewusstsein verankert zu sein, dass er sich nicht manipulieren ließe, wenn es darauf ankommt? Wer griffe nicht in der Verzweiflung nach einem Heiligenbild, das am Himmel aufsteigt? Wer wäre erhaben über jede Art von Mind Control?
So möge der stille werden, der sich rühmt, erwacht zu sein. Möge er sich den Schlaf aus den Augen reiben und sich an die Arbeit machen. Denn das Erwachen ist nur der allererste Schritt. Dann geht es erst richtig los.
Dann können wir üben, in die Selbstwirksamkeit zu kommen: das Vertrauen in die eigenen Möglichkeiten, Aufgabenanforderungen wirksam zu bewältigen und auch in Extremsituationen gewünschte Handlungen selbst ausführen zu können.
Die Frage ist nicht, wie erwacht wir uns im Vergleich mit anderen fühlen, sondern welches Selbst- und Menschenbild wir haben und wie wir von unserer natürlichen Schöpferkraft Gebrauch machen. Nicht der ist erwacht, der sich von Katastrophenmeldungen einlullen lässt und sich gemütlich in seinen vier Wänden auf den Weltuntergang vorbereitet, sondern der, der sich darauf besinnt, dass Bewusstsein mehr ist als ein paar Synapsen im Gehirn. Er weiß, dass er über einen freien Willen verfügt, der ihn dazu befähigt, in eine andere Richtung zu gehen.
Außen wie innen
Bewusstsein hängt von keinem spirituellen Führer ab und auch von keinem Gott, der in den Himmel projiziert wird. Bewusstsein ist göttlich. Es ist die Fähigkeit, Dinge wahr-zu-nehmen, ihren Wahrheitsgehalt zu erkennen, die Gabe, aus sich heraus feinfühlig zu sein, hellsichtig, verstehend. Im individuellen Bewusstsein sind das Menschliche und das Göttliche eins. Nichts steht trennend dazwischen. Niemand muss die Erlaubnis für diesen Erkenntnisprozess geben.
Wer bei Bewusstsein ist, den kann man nicht in ein Gedankengefängnis einsperren oder ihn mit Hierarchien beeindrucken. Er weiß, dass das Wesentliche sich im Innen abspielt und dass allein er für das verantwortlich ist, was er erlebt.
Ein hoch entwickeltes Bewusstsein bedeutet, sich von jeder Erwartung zu lösen, dass sich im Außen etwas ändert. Wer sich auf das Außen konzentriert, der hat schon verloren. Er drückt sich selbst den Stempel der Ohnmacht und des Mangels auf oder befeuert die Kriegsmaschinerie, die alles in die Zerstörung treibt.
Im Inneren gilt es, für Harmonie zu sorgen und sich auf die Frequenzen des Schöpferischen einzustellen. So darf sich jeder fragen: Wie sieht es bei mir aus? Bin ich von Menschen umgeben, die mich erniedrigen oder die mich erhöhen? Lebe ich das Leben, das ich mir wünsche? Bin ich im Mangel oder im Überfluss? Bin ich krank oder gesund? Ängstlich oder vertrauend? Zynisch oder liebevoll? Wie halte ich es? Wie ist meine Stimmung? Wie fühle ich mich in dieser Zeit, in dieser Welt? Wage ich es, Nein zu sagen, wenn alle Ja sagen, und Ja, wenn alle Nein sagen?
Wie selbstwirksam bin ich? Wie benutze ich die mir angeborene Schöpferkraft? Lasse ich mit mir machen oder mache ich selbst? Welche Menschen und Ereignisse ziehe ich an? Auf welcher Ebene schwingt meine Energie? Mit welchen Kräften stehe ich in Kontakt? Welche Informationen empfange ich? Wie viel Individualität wage ich? Nicht eine Individualität, die andere ausschließt, sondern eine, die alles miteinschließt und von dem Bewusstsein geleitet wird, dass alles eins ist.
Fühle ich mich getrennt oder verbunden? Fühle ich, dass ich unteilbar bin: in-dividuum? Spüre ich, wie ich aus der Kraft dieser Unteilbarkeit heraus unermessliche Möglichkeiten habe, mein Leben und damit die Welt zu gestalten? Bin ich wirklich erwacht oder halte ich mich nur für etwas Besseres, um bei der nächstbesten Gelegenheit genau das zu tun, was ich an anderen kritisiert habe: mein Heil von außen zu erwarten?
Angst- oder Christusmatrix?
Was auch kommt in der nächsten Zeit: Es wird uns überraschen. Jede Menge Möglichkeiten wird es geben, in denen wir unser Bewusstsein und unsere Individualität auf die Probe stellen können. Auf uns kommt es an! Jeder Mensch, der sich selbst aus der Ohnmacht befreit, befreit auch die Welt ein wenig mehr. Jeder, der sich nicht von schlechten Nachrichten nach unten ziehen lässt, jeder, der darauf achtet, seine Energie möglichst hoch schwingen zu lassen, jeder, der in sich selbst die Lösung sucht, ist ein Segen für diese Zeit, ein Tor für das Göttliche auf Erden.
Göttlich, so die Bewusstseinstrainerin Sandra Weber, ist alles, was natürlich ist, alles, was liebt, was pulsiert, leuchtet und verbunden ist. Wir haben die Wahl, uns per Genmanipulation und künstlicher Intelligenz (KI) immer mehr entmenschlichen zu lassen oder unser multidimensionales Potenzial zu entdecken, unsere Fähigkeit zu Telepathie, Telekinese und Teleportation. Angst- oder Christusmatrix — wofür entscheiden wir uns? Lassen wir durch KI die eigene Lichtkörperaktivierung unterbrechen oder wählen wir die Erhebung und das Vertrauen in unsere Göttlichkeit (3)?
Von hier aus können wir die Bühne überblicken. Wir erkennen: Wir müssen da nicht mitmachen. Wir müssen nicht in das Welttheater einsteigen. Wir müssen nicht die Lichtschwerter auspacken und für das Gute kämpfen. Das Gute kämpft nicht. Das Gute ist. Was wir tun können, ist, uns von den Altlasten zu befreien, die uns unten halten, innere Kämpfe ein für alle Mal zu befrieden und unsere Schatten ins Licht zu bringen.
Erleuchtung ist, wenn die inneren Schatten aufgelöst sind und man alles überblicken kann. Er-innern wir uns. Gehen wir nach innen und bauen wir hier unsere Tempel.
Fassen wir den Mut, wir selbst zu sein. Gehen wir in unsere Herzensmitte, werden wir uns der Bewertungen bewusst, mit der wir unsere Welt in Gut und Böse einteilen, und nehmen wir einen neutralen Standpunkt ein. So kommen wir aus der Dualität zurück in die Polarität, aus einer Welt, in der sich die Dinge gegenseitig vernichten, in eine Welt, in der sie sich ergänzen und kreativ zusammenwirken.
Quellen und Anmerkungen:
(1) https://lexikon.stangl.eu/887/bewusstsein\ (2) https://de.wikipedia.org/wiki/Gehirnw%C3%A4sche\ (3) https://www.youtube.com/watch?v=grAFeprqzhs&t=13s
Kerstin Chavent ist Sprachlehrerin und lebt in Südfrankreich. Sie schreibt Artikel, Essays und autobiographische Erzählungen. Ihre Schwerpunkte sind der Umgang mit Krisensituationen und Krankheit und die Sensibilisierung für das schöpferische Potential im Menschen. Auf Deutsch erschienen sind Die wilde Göttin, Der Königsweg, Die Enthüllung, In guter Gesellschaft, Die Waffen niederlegen, Das Licht fließt dahin, wo es dunkel ist, Krankheit heilt, Was wachsen will muss Schalen abwerfen, Und Freitags kommt der Austernwagen. Weitere Informationen auf kerstinchavent.de.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 30ceb64e:7f08bdf5
2025-04-26 20:33:30
@ 30ceb64e:7f08bdf5
2025-04-26 20:33:30Status: Draft
Author: TheWildHustleAbstract
This NIP defines a framework for storing and sharing health and fitness profile data on Nostr. It establishes a set of standardized event kinds for individual health metrics, allowing applications to selectively access specific health information while preserving user control and privacy.
In this framework exists - NIP-101h.1 Weight using kind 1351 - NIP-101h.2 Height using kind 1352 - NIP-101h.3 Age using kind 1353 - NIP-101h.4 Gender using kind 1354 - NIP-101h.5 Fitness Level using kind 1355
Motivation
I want to build and support an ecosystem of health and fitness related nostr clients that have the ability to share and utilize a bunch of specific interoperable health metrics.
- Selective access - Applications can access only the data they need
- User control - Users can choose which metrics to share
- Interoperability - Different health applications can share data
- Privacy - Sensitive health information can be managed independently
Specification
Kind Number Range
Health profile metrics use the kind number range 1351-1399:
| Kind | Metric | | --------- | ---------------------------------- | | 1351 | Weight | | 1352 | Height | | 1353 | Age | | 1354 | Gender | | 1355 | Fitness Level | | 1356-1399 | Reserved for future health metrics |
Common Structure
All health metric events SHOULD follow these guidelines:
- The content field contains the primary value of the metric
- Required tags:
['t', 'health']- For categorizing as health data['t', metric-specific-tag]- For identifying the specific metric['unit', unit-of-measurement]- When applicable- Optional tags:
['converted_value', value, unit]- For providing alternative unit measurements['timestamp', ISO8601-date]- When the metric was measured['source', application-name]- The source of the measurement
Unit Handling
Health metrics often have multiple ways to be measured. To ensure interoperability:
- Where multiple units are possible, one standard unit SHOULD be chosen as canonical
- When using non-standard units, a
converted_valuetag SHOULD be included with the canonical unit - Both the original and converted values should be provided for maximum compatibility
Client Implementation Guidelines
Clients implementing this NIP SHOULD:
- Allow users to explicitly choose which metrics to publish
- Support reading health metrics from other users when appropriate permissions exist
- Support updating metrics with new values over time
- Preserve tags they don't understand for future compatibility
- Support at least the canonical unit for each metric
Extensions
New health metrics can be proposed as extensions to this NIP using the format:
- NIP-101h.X where X is the metric number
Each extension MUST specify: - A unique kind number in the range 1351-1399 - The content format and meaning - Required and optional tags - Examples of valid events
Privacy Considerations
Health data is sensitive personal information. Clients implementing this NIP SHOULD:
- Make it clear to users when health data is being published
- Consider incorporating NIP-44 encryption for sensitive metrics
- Allow users to selectively share metrics with specific individuals
- Provide easy ways to delete previously published health data
NIP-101h.1: Weight
Description
This NIP defines the format for storing and sharing weight data on Nostr.
Event Kind: 1351
Content
The content field MUST contain the numeric weight value as a string.
Required Tags
- ['unit', 'kg' or 'lb'] - Unit of measurement
- ['t', 'health'] - Categorization tag
- ['t', 'weight'] - Specific metric tag
Optional Tags
- ['converted_value', value, unit] - Provides the weight in alternative units for interoperability
- ['timestamp', ISO8601 date] - When the weight was measured
Examples
json { "kind": 1351, "content": "70", "tags": [ ["unit", "kg"], ["t", "health"], ["t", "weight"] ] }json { "kind": 1351, "content": "154", "tags": [ ["unit", "lb"], ["t", "health"], ["t", "weight"], ["converted_value", "69.85", "kg"] ] }NIP-101h.2: Height
Status: Draft
Description
This NIP defines the format for storing and sharing height data on Nostr.
Event Kind: 1352
Content
The content field can use two formats: - For metric height: A string containing the numeric height value in centimeters (cm) - For imperial height: A JSON string with feet and inches properties
Required Tags
['t', 'health']- Categorization tag['t', 'height']- Specific metric tag['unit', 'cm' or 'imperial']- Unit of measurement
Optional Tags
['converted_value', value, 'cm']- Provides height in centimeters for interoperability when imperial is used['timestamp', ISO8601-date]- When the height was measured
Examples
```jsx // Example 1: Metric height Apply to App.jsx
// Example 2: Imperial height with conversion Apply to App.jsx ```
Implementation Notes
- Centimeters (cm) is the canonical unit for height interoperability
- When using imperial units, a conversion to centimeters SHOULD be provided
- Height values SHOULD be positive integers
- For maximum compatibility, clients SHOULD support both formats
NIP-101h.3: Age
Status: Draft
Description
This NIP defines the format for storing and sharing age data on Nostr.
Event Kind: 1353
Content
The content field MUST contain the numeric age value as a string.
Required Tags
['unit', 'years']- Unit of measurement['t', 'health']- Categorization tag['t', 'age']- Specific metric tag
Optional Tags
['timestamp', ISO8601-date]- When the age was recorded['dob', ISO8601-date]- Date of birth (if the user chooses to share it)
Examples
```jsx // Example 1: Basic age Apply to App.jsx
// Example 2: Age with DOB Apply to App.jsx ```
Implementation Notes
- Age SHOULD be represented as a positive integer
- For privacy reasons, date of birth (dob) is optional
- Clients SHOULD consider updating age automatically if date of birth is known
- Age can be a sensitive metric and clients may want to consider encrypting this data
NIP-101h.4: Gender
Status: Draft
Description
This NIP defines the format for storing and sharing gender data on Nostr.
Event Kind: 1354
Content
The content field contains a string representing the user's gender.
Required Tags
['t', 'health']- Categorization tag['t', 'gender']- Specific metric tag
Optional Tags
['timestamp', ISO8601-date]- When the gender was recorded['preferred_pronouns', string]- User's preferred pronouns
Common Values
While any string value is permitted, the following common values are recommended for interoperability: - male - female - non-binary - other - prefer-not-to-say
Examples
```jsx // Example 1: Basic gender Apply to App.jsx
// Example 2: Gender with pronouns Apply to App.jsx ```
Implementation Notes
- Clients SHOULD allow free-form input for gender
- For maximum compatibility, clients SHOULD support the common values
- Gender is a sensitive personal attribute and clients SHOULD consider appropriate privacy controls
- Applications focusing on health metrics should be respectful of gender diversity
NIP-101h.5: Fitness Level
Status: Draft
Description
This NIP defines the format for storing and sharing fitness level data on Nostr.
Event Kind: 1355
Content
The content field contains a string representing the user's fitness level.
Required Tags
['t', 'health']- Categorization tag['t', 'fitness']- Fitness category tag['t', 'level']- Specific metric tag
Optional Tags
['timestamp', ISO8601-date]- When the fitness level was recorded['activity', activity-type]- Specific activity the fitness level relates to['metrics', JSON-string]- Quantifiable fitness metrics used to determine level
Common Values
While any string value is permitted, the following common values are recommended for interoperability: - beginner - intermediate - advanced - elite - professional
Examples
```jsx // Example 1: Basic fitness level Apply to App.jsx
// Example 2: Activity-specific fitness level with metrics Apply to App.jsx ```
Implementation Notes
- Fitness level is subjective and may vary by activity
- The activity tag can be used to specify fitness level for different activities
- The metrics tag can provide objective measurements to support the fitness level
- Clients can extend this format to include activity-specific fitness assessments
- For general fitness apps, the simple beginner/intermediate/advanced scale is recommended
-
 @ 57d1a264:69f1fee1
2025-05-05 05:26:34
@ 57d1a264:69f1fee1
2025-05-05 05:26:34The European Accessibility Act is coming, now is a great time for accessibility trainings!. In my Accessibility for Designer workshop, you will learn how to design accessible mockups that prevent issues in visual design, interactions, navigation, and content. You will be able to spot problems early, fix them in your designs, and communicate accessibility clearly with your team. This is a practical workshop with hands-on exercises, not just theory. You’ll actively apply accessibility principles to real design scenarios and mockups. And will get access to my accessibility resources: checklists, annotation kits and more.
When? 4 sessions of 2 hours + Q and As, on: - Mon, June 16, - Tue, June 17, Mon, - June 23 and Tue, - June 24. 9:30 – 12:00 PM PT or 18:30 – 21:00 CET
Register with 15% discount ($255) https://ti.to/smashingmagazine/online-workshops-2022/with/87vynaoqc0/discount/welcometomyworkshop
originally posted at https://stacker.news/items/971772
-
 @ 9223d2fa:b57e3de7
2025-05-09 18:35:00
@ 9223d2fa:b57e3de7
2025-05-09 18:35:0014,227 steps
-
 @ 000002de:c05780a7
2025-05-09 18:33:06
@ 000002de:c05780a7
2025-05-09 18:33:06I've been eager to share my thoughts on "Return of the Strong Gods" by R.R. Reno since I finished it a week ago.
I found this book incredibly insightful. @SimpleStacker's excellent review prompted me to pick it up, and I'm glad I did. While I won't be providing a full review, I will share some of the key insights and thoughts that resonated with me.
Reno masterfully dissects the sociological underpinnings of the political shifts in the US and the Western world over the past decade and a half. His analysis of the rise of populism and nationalism is compelling and rings true to my personal observations. Reno's central thesis is that post-WW2, the West embraced "weaker gods"—ideals like democracy, pluralism, and liberalism—fearing a repeat of the strong nationalistic sentiments that led to Hitler's rise. He argues that this shift has left many people feeling culturally homeless and desperate for strong leadership that listens to their grievances.
A significant portion of Reno's argument is built on the ideas of Karl Popper, a philosopher I was unfamiliar with before reading this book. Popper's work "The Open Society and Its Enemies" has significantly influenced post-war consensus, which Reno argues has led to a disconnect between the political elite and the common people. This disconnect, he posits, is a primary driver of populist sentiments.
Reno also delves into economics, discussing Friedrich Hayek and his agreement with some of Popper's positions. This intersection of philosophy and economics provides a unique lens through which to view the political landscape. Reno's mention of the Treaty of Versailles as a catalyst for Hitler's rise is a point often overlooked in discussions about WW2. He argues that the punitive measures imposed on Germany created an environment ripe for a strongman to emerge.
One of the most compelling aspects of Reno's argument is his explanation of how the political elite often lose touch with the values and wishes of the people they represent. He draws a powerful analogy between cultural homelessness and the desperation that drives people to seek strong leadership. This section of the book particularly resonated with me, as it aligns with my own observations of the political climate.
I would have liked Reno to start his analysis with Woodrow Wilson, whose "making the world safe for democracy" slogan embodied a form of Christian nationalism. Wilson's ideals and the post-WW1 environment laid the groundwork for the open society movement, which Reno critiques. Exploring this historical context could have strengthened Reno's argument.
Reno occasionally conflates economic liberalism with libertinism, which I found to be a minor flaw in an otherwise strong argument. He rightly points out the need for moral ethics in society but seems to overlook the distinction between economic freedom and moral laxity. Reno's discussion of Milton Friedman's ideas further highlights this confusion. While Reno argues that free trade has contributed to many of our modern ills, I believe the issue lies more with nation-state trade agreements like NAFTA, which are not true examples of free trade.
Another area where I disagree with Reno is his conflation of the nation with the state. Nations are cultural entities that predate and can exist independently of states. Reno's argument would be stronger if he acknowledged this distinction, as it would clarify his points about national pride and cultural heritage.
Reno's final chapters offer a cautionary tale about the return of strong gods and the danger of making them idols. He warns against authoritarianism and the overreach of the state, advocating for a balance that respects cultural heritage without succumbing to nationalism.
In conclusion, "Return of the Strong Gods" is a thought-provoking exploration of the political and cultural shifts of our time. Reno's insights are valuable, and his arguments, while not without flaws, provide a fresh perspective on the rise of populism and nationalism. I recommend this book to anyone seeking a deeper understanding of the forces shaping our world today.
originally posted at https://stacker.news/items/975849
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 6146ad04:a0937b0b
2025-05-09 09:06:45
@ 6146ad04:a0937b0b
2025-05-09 09:06:45In the rapidly evolving world of technology, edge computing has emerged as a game-changing innovation, reshaping how data is processed, analyzed, and delivered. Unlike traditional cloud computing, which relies on centralized data centers, edge computing processes data closer to the source—right where it's generated.
This shift is driven by the explosion of Internet of Things (IoT) devices, autonomous systems, and real-time applications that demand low latency and fast decision-making. From smart factories and self-driving cars to remote healthcare and AR/VR experiences, the need for real-time processing is fueling the growth of edge solutions.
Why Edge Computing Matters
As more devices connect to the internet, the volume of data being generated is staggering. Transmitting all this data to the cloud for processing can introduce delays and raise bandwidth costs. Edge computing addresses these challenges by enabling devices and local servers to handle tasks immediately, without having to send data back and forth to the cloud.
Key benefits include:
Reduced latency: Ideal for time-sensitive applications like autonomous vehicles and industrial automation.
Improved security: Sensitive data can be processed locally, minimizing exposure.
Cost efficiency: Reduces bandwidth and storage demands on central data centers.
Real-World Applications
-
Healthcare: Wearables and remote monitoring devices use edge computing to detect anomalies and alert physicians in real time.
-
Retail: Smart shelves and AI-powered cameras analyze consumer behavior on the spot.
-
Manufacturing: Machines use edge-based analytics to predict maintenance needs and prevent downtime.
Challenges Ahead
Despite its promise, edge computing is not without hurdles. Managing a distributed network of devices, ensuring consistent software updates, and maintaining security at the edge require robust frameworks and standards. Scalability and interoperability remain ongoing concerns for developers and organizations.
The Road Ahead
With the rollout of 5G and advancements in AI, edge computing is poised for massive growth. According to industry forecasts, the global edge computing market is expected to exceed $100 billion by 2030. As businesses continue to demand faster, smarter, and more secure tech infrastructure, edge computing will be at the heart of the next digital transformation.
-
-
 @ 8125b911:a8400883
2025-04-25 07:02:35
@ 8125b911:a8400883
2025-04-25 07:02:35In Nostr, all data is stored as events. Decentralization is achieved by storing events on multiple relays, with signatures proving the ownership of these events. However, if you truly want to own your events, you should run your own relay to store them. Otherwise, if the relays you use fail or intentionally delete your events, you'll lose them forever.
For most people, running a relay is complex and costly. To solve this issue, I developed nostr-relay-tray, a relay that can be easily run on a personal computer and accessed over the internet.
Project URL: https://github.com/CodyTseng/nostr-relay-tray
This article will guide you through using nostr-relay-tray to run your own relay.
Download
Download the installation package for your operating system from the GitHub Release Page.
| Operating System | File Format | | --------------------- | ---------------------------------- | | Windows |
nostr-relay-tray.Setup.x.x.x.exe| | macOS (Apple Silicon) |nostr-relay-tray-x.x.x-arm64.dmg| | macOS (Intel) |nostr-relay-tray-x.x.x.dmg| | Linux | You should know which one to use |Installation
Since this app isn’t signed, you may encounter some obstacles during installation. Once installed, an ostrich icon will appear in the status bar. Click on the ostrich icon, and you'll see a menu where you can click the "Dashboard" option to open the relay's control panel for further configuration.

macOS Users:
- On first launch, go to "System Preferences > Security & Privacy" and click "Open Anyway."
- If you encounter a "damaged" message, run the following command in the terminal to remove the restrictions:
bash sudo xattr -rd com.apple.quarantine /Applications/nostr-relay-tray.appWindows Users:
- On the security warning screen, click "More Info > Run Anyway."
Connecting
By default, nostr-relay-tray is only accessible locally through
ws://localhost:4869/, which makes it quite limited. Therefore, we need to expose it to the internet.In the control panel, click the "Proxy" tab and toggle the switch. You will then receive a "Public address" that you can use to access your relay from anywhere. It's that simple.
Next, add this address to your relay list and position it as high as possible in the list. Most clients prioritize connecting to relays that appear at the top of the list, and relays lower in the list are often ignored.

Restrictions
Next, we need to set up some restrictions to prevent the relay from storing events that are irrelevant to you and wasting storage space. nostr-relay-tray allows for flexible and fine-grained configuration of which events to accept, but some of this is more complex and will not be covered here. If you're interested, you can explore this further later.
For now, I'll introduce a simple and effective strategy: WoT (Web of Trust). You can enable this feature in the "WoT & PoW" tab. Before enabling, you'll need to input your pubkey.
There's another important parameter,
Depth, which represents the relationship depth between you and others. Someone you follow has a depth of 1, someone they follow has a depth of 2, and so on.- Setting this parameter to 0 means your relay will only accept your own events.
- Setting it to 1 means your relay will accept events from you and the people you follow.
- Setting it to 2 means your relay will accept events from you, the people you follow, and the people they follow.
Currently, the maximum value for this parameter is 2.

Conclusion
You've now successfully run your own relay and set a simple restriction to prevent it from storing irrelevant events.
If you encounter any issues during use, feel free to submit an issue on GitHub, and I'll respond as soon as possible.
Not your relay, not your events.
-
 @ a5ee4475:2ca75401
2025-05-09 17:13:22
@ a5ee4475:2ca75401
2025-05-09 17:13:22lista #descentralismo #compilado #portugues
*Algumas destas listas ainda estão sendo trocadas, portanto as versões mais recentes delas só estão visíveis no Amethyst por causa da ferramenta de edição.
Clients do Nostr e Outras Coisas
nostr:naddr1qq245dz5tqe8w46swpphgmr4f3047s6629t45qg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guxde6sl
Modelos de IA e Ferramentas
nostr:naddr1qq24xwtyt9v5wjzefe6523j32dy5ga65gagkjqgswaehxw309ahx7um5wghx6mmd9upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guk62czu
Iniciativas de Bitcoin
nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2nvmn5va9x2nrxfd2k5smyf3ux7vesd9znyqxygt4
Profissionais Brasileiros no Nostr
nostr:naddr1qq24qmnkwe6y67zlxgc4sumrxpxxce3kf9fn2qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7q3q5hhygatg5gmjyfkkguqn54f9r6k8m5m6ksyqffgjrf3uut982sqsxpqqqp65wp8uedu
Comunidades em Português no Nostr
nostr:naddr1qq2hwcejv4ykgdf3v9gxykrxfdqk753jxcc4gqg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4gu455fm3
Grupos em Português no Nostr
nostr:nevent1qqs98kldepjmlxngupsyth40n0h5lw7z5ut5w4scvh27alc0w86tevcpzpmhxue69uhkummnw3ezumt0d5hsygy7fff8g6l23gp5uqtuyqwkqvucx6mhe7r9h7v6wyzzj0v6lrztcspsgqqqqqqs3ndneh
Jogos de Código Aberto
Open Source Games nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2kvwp3v4hhvk2sw3j5sm6h23g5wkz5ddzhz8x40v0
Formatação de Texto em Markdown
(Amethyst, Yakihone e outros) nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2454m8dfzn26z4f34kvu6fw4rysnrjxfm42wfpe90
Outros Links
nostr:nevent1qqsrm6ywny5r7ajakpppp0lt525n0s33x6tyn6pz0n8ws8k2tqpqracpzpmhxue69uhkummnw3ezumt0d5hsygp6e5ns0nv3dun430jky25y4pku6ylz68rz6zs7khv29q6rj5peespsgqqqqqqsmfwa78
-
 @ 84b0c46a:417782f5
2025-05-10 10:41:20
@ 84b0c46a:417782f5
2025-05-10 10:41:20https://long-form-editor.vercel.app/
β版のため予期せぬ動作が発生する可能性があります。記事を修正する際は事前にバックアップを取ることをおすすめします
機能
-
nostr:npub1sjcvg64knxkrt6ev52rywzu9uzqakgy8ehhk8yezxmpewsthst6sw3jqcw や、 nostr:nevent1qvzqqqqqqypzq4jsz7zew5j7jr4pdfxh483nwq9vyw9ph6wm706sjwrzj2we58nqqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyxhwumn8ghj7mn0wvhxcmmvqqsgcn99jyn5tevxz5zxsrkd7h0sx8fwnqztula423xh83j9wau7cms3vg9c7 のようにnostr:要素を挿入できる
-
:monoice:のようにカスタム絵文字を挿入できる(メニューの😃アイコンから←アイコン変えるかも)
:monopaca_kao:
:kubipaca_karada:
- 新規記事作成と、既存記事の修正ができる
やることやったこと
-
[x] nostr:を投稿するときにtagにいれる
-
[x] 画像をアップロードできるようにする
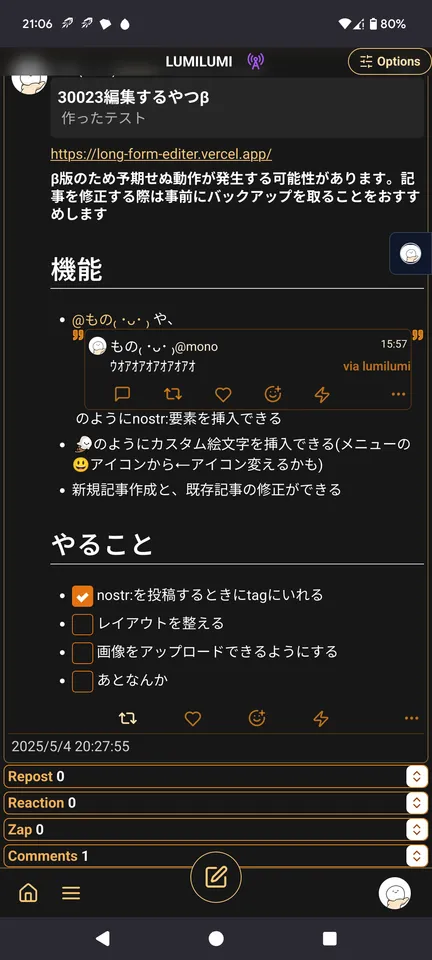 できる
できる - [x] 投稿しましたログとかをトースト的なやつでだすようにする
- [ ] レイアウトを整える
- [ ] あとなんか
-
-
 @ e691f4df:1099ad65
2025-04-24 18:56:12
@ e691f4df:1099ad65
2025-04-24 18:56:12Viewing Bitcoin Through the Light of Awakening
Ankh & Ohm Capital’s Overview of the Psycho-Spiritual Nature of Bitcoin
Glossary:
I. Preface: The Logos of Our Logo
II. An Oracular Introduction
III. Alchemizing Greed
IV. Layers of Fractalized Thought
V. Permissionless Individuation
VI. Dispelling Paradox Through Resonance
VII. Ego Deflation
VIII. The Coin of Great Price
Preface: The Logos of Our Logo
Before we offer our lens on Bitcoin, it’s important to illuminate the meaning behind Ankh & Ohm’s name and symbol. These elements are not ornamental—they are foundational, expressing the cosmological principles that guide our work.
Our mission is to bridge the eternal with the practical. As a Bitcoin-focused family office and consulting firm, we understand capital not as an end, but as a tool—one that, when properly aligned, becomes a vehicle for divine order. We see Bitcoin not simply as a technological innovation but as an emanation of the Divine Logos—a harmonic expression of truth, transparency, and incorruptible structure. Both the beginning and the end, the Alpha and Omega.
The Ankh (☥), an ancient symbol of eternal life, is a key to the integration of opposites. It unites spirit and matter, force and form, continuity and change. It reminds us that capital, like Life, must not only be generative, but regenerative; sacred. Money must serve Life, not siphon from it.
The Ohm (Ω) holds a dual meaning. In physics, it denotes a unit of electrical resistance—the formative tension that gives energy coherence. In the Vedic tradition, Om (ॐ) is the primordial vibration—the sound from which all existence unfolds. Together, these symbols affirm a timeless truth: resistance and resonance are both sacred instruments of the Creator.
Ankh & Ohm, then, represents our striving for union, for harmony —between the flow of life and intentional structure, between incalculable abundance and measured restraint, between the lightbulb’s electrical impulse and its light-emitting filament. We stand at the threshold where intention becomes action, and where capital is not extracted, but cultivated in rhythm with the cosmos.
We exist to shepherd this transformation, as guides of this threshold —helping families, founders, and institutions align with a deeper order, where capital serves not as the prize, but as a pathway to collective Presence, Purpose, Peace and Prosperity.
An Oracular Introduction
Bitcoin is commonly understood as the first truly decentralized and secure form of digital money—a breakthrough in monetary sovereignty. But this view, while technically correct, is incomplete and spiritually shallow. Bitcoin is more than a tool for economic disruption. Bitcoin represents a mythic threshold: a symbol of the psycho-spiritual shift that many ancient traditions have long foretold.
For millennia, sages and seers have spoken of a coming Golden Age. In the Vedic Yuga cycles, in Plato’s Great Year, in the Eagle and Condor prophecies of the Americas—there exists a common thread: that humanity will emerge from darkness into a time of harmony, cooperation, and clarity. That the veil of illusion (maya, materiality) will thin, and reality will once again become transparent to the transcendent. In such an age, systems based on scarcity, deception, and centralization fall away. A new cosmology takes root—one grounded in balance, coherence, and sacred reciprocity.
But we must ask—how does such a shift happen? How do we cross from the age of scarcity, fear, and domination into one of coherence, abundance, and freedom?
One possible answer lies in the alchemy of incentive.
Bitcoin operates not just on the rules of computer science or Austrian economics, but on something far more old and subtle: the logic of transformation. It transmutes greed—a base instinct rooted in scarcity—into cooperation, transparency, and incorruptibility.
In this light, Bitcoin becomes more than code—it becomes a psychoactive protocol, one that rewires human behavior by aligning individual gain with collective integrity. It is not simply a new form of money. It is a new myth of value. A new operating system for human consciousness.
Bitcoin does not moralize. It harmonizes. It transforms the instinct for self-preservation into a pathway for planetary coherence.
Alchemizing Greed
At the heart of Bitcoin lies the ancient alchemical principle of transmutation: that which is base may be refined into gold.
Greed, long condemned as a vice, is not inherently evil. It is a distorted longing. A warped echo of the drive to preserve life. But in systems built on scarcity and deception, this longing calcifies into hoarding, corruption, and decay.
Bitcoin introduces a new game. A game with memory. A game that makes deception inefficient and truth profitable. It does not demand virtue—it encodes consequence. Its design does not suppress greed; it reprograms it.
In traditional models, game theory often illustrates the fragility of trust. The Prisoner’s Dilemma reveals how self-interest can sabotage collective well-being. But Bitcoin inverts this. It creates an environment where self-interest and integrity converge—where the most rational action is also the most truthful.
Its ledger, immutable and transparent, exposes manipulation for what it is: energetically wasteful and economically self-defeating. Dishonesty burns energy and yields nothing. The network punishes incoherence, not by decree, but by natural law.
This is the spiritual elegance of Bitcoin: it does not suppress greed—it transmutes it. It channels the drive for personal gain into the architecture of collective order. Miners compete not to dominate, but to validate. Nodes collaborate not through trust, but through mathematical proof.
This is not austerity. It is alchemy.
Greed, under Bitcoin, is refined. Tempered. Re-forged into a generative force—no longer parasitic, but harmonic.
Layers of Fractalized Thought Fragments
All living systems are layered. So is the cosmos. So is the human being. So is a musical scale.
At its foundation lies the timechain—the pulsing, incorruptible record of truth. Like the heart, it beats steadily. Every block, like a pulse, affirms its life through continuity. The difficulty adjustment—Bitcoin’s internal calibration—functions like heart rate variability, adapting to pressure while preserving coherence.
Above this base layer is the Lightning Network—a second layer facilitating rapid, efficient transactions. It is the nervous system: transmitting energy, reducing latency, enabling real-time interaction across a distributed whole.
Beyond that, emerging tools like Fedimint and Cashu function like the capillaries—bringing vitality to the extremities, to those underserved by legacy systems. They empower the unbanked, the overlooked, the forgotten. Privacy and dignity in the palms of those the old system refused to see.
And then there is NOSTR—the decentralized protocol for communication and creation. It is the throat chakra, the vocal cords of the “freedom-tech” body. It reclaims speech from the algorithmic overlords, making expression sovereign once more. It is also the reproductive system, as it enables the propagation of novel ideas and protocols in fertile, uncensorable soil.
Each layer plays its part. Not in hierarchy, but in harmony. In holarchy. Bitcoin and other open source protocols grow not through exogenous command, but through endogenous coherence. Like cells in an organism. Like a song.
Imagine the cell as a piece of glass from a shattered holographic plate —by which its perspectival, moving image can be restructured from the single shard. DNA isn’t only a logical script of base pairs, but an evolving progressive song. Its lyrics imbued with wise reflections on relationships. The nucleus sings, the cell responds—not by command, but by memory. Life is not imposed; it is expressed. A reflection of a hidden pattern.
Bitcoin chants this. Each node, a living cell, holds the full timechain—Truth distributed, incorruptible. Remove one, and the whole remains. This isn’t redundancy. It’s a revelation on the power of protection in Truth.
Consensus is communion. Verification becomes a sacred rite—Truth made audible through math.
Not just the signal; the song. A web of self-expression woven from Truth.
No center, yet every point alive with the whole. Like Indra’s Net, each reflects all. This is more than currency and information exchange. It is memory; a self-remembering Mind, unfolding through consensus and code. A Mind reflecting the Truth of reality at the speed of thought.
Heuristics are mental shortcuts—efficient, imperfect, alive. Like cells, they must adapt or decay. To become unbiased is to have self-balancing heuristics which carry feedback loops within them: they listen to the environment, mutate when needed, and survive by resonance with reality. Mutation is not error, but evolution. Its rules are simple, but their expression is dynamic.
What persists is not rigidity, but pattern.
To think clearly is not necessarily to be certain, but to dissolve doubt by listening, adjusting, and evolving thought itself.
To understand Bitcoin is simply to listen—patiently, clearly, as one would to a familiar rhythm returning.
Permissionless Individuation
Bitcoin is a path. One that no one can walk for you.
Said differently, it is not a passive act. It cannot be spoon-fed. Like a spiritual path, it demands initiation, effort, and the willingness to question inherited beliefs.
Because Bitcoin is permissionless, no one can be forced to adopt it. One must choose to engage it—compelled by need, interest, or intuition. Each person who embarks undergoes their own version of the hero’s journey.
Carl Jung called this process Individuation—the reconciliation of fragmented psychic elements into a coherent, mature Self. Bitcoin mirrors this: it invites individuals to confront the unconscious assumptions of the fiat paradigm, and to re-integrate their relationship to time, value, and agency.
In Western traditions—alchemy, Christianity, Kabbalah—the individual is sacred, and salvation is personal. In Eastern systems—Daoism, Buddhism, the Vedas—the self is ultimately dissolved into the cosmic whole. Bitcoin, in a paradoxical way, echoes both: it empowers the individual, while aligning them with a holistic, transcendent order.
To truly see Bitcoin is to allow something false to die. A belief. A habit. A self-concept.
In that death—a space opens for deeper connection with the Divine itSelf.
In that dissolution, something luminous is reborn.
After the passing, Truth becomes resurrected.
Dispelling Paradox Through Resonance
There is a subtle paradox encoded into the hero’s journey: each starts in solidarity, yet the awakening affects the collective.
No one can be forced into understanding Bitcoin. Like a spiritual truth, it must be seen. And yet, once seen, it becomes nearly impossible to unsee—and easier for others to glimpse. The pattern catches.
This phenomenon mirrors the concept of morphic resonance, as proposed and empirically tested by biologist Rupert Sheldrake. Once a critical mass of individuals begins to embody a new behavior or awareness, it becomes easier—instinctive—for others to follow suit. Like the proverbial hundredth monkey who begins to wash the fruit in the sea water, and suddenly, monkeys across islands begin doing the same—without ever meeting.
When enough individuals embody a pattern, it ripples outward. Not through propaganda, but through field effect and wave propagation. It becomes accessible, instinctive, familiar—even across great distance.
Bitcoin spreads in this way. Not through centralized broadcast, but through subtle resonance. Each new node, each individual who integrates the protocol into their life, strengthens the signal for others. The protocol doesn’t shout; it hums, oscillates and vibrates——persistently, coherently, patiently.
One awakens. Another follows. The current builds. What was fringe becomes familiar. What was radical becomes obvious.
This is the sacred geometry of spiritual awakening. One awakens, another follows, and soon the fluidic current is strong enough to carry the rest. One becomes two, two become many, and eventually the many become One again. This tessellation reverberates through the human aura, not as ideology, but as perceivable pattern recognition.
Bitcoin’s most powerful marketing tool is truth. Its most compelling evangelist is reality. Its most unstoppable force is resonance.
Therefore, Bitcoin is not just financial infrastructure—it is psychic scaffolding. It is part of the subtle architecture through which new patterns of coherence ripple across the collective field.
The training wheels from which humanity learns to embody Peace and Prosperity.
Ego Deflation
The process of awakening is not linear, and its beginning is rarely gentle—it usually begins with disruption, with ego inflation and destruction.
To individuate is to shape a center; to recognize peripherals and create boundaries—to say, “I am.” But without integration, the ego tilts—collapsing into void or inflating into noise. Fiat reflects this pathology: scarcity hoarded, abundance simulated. Stagnation becomes disguised as safety, and inflation masquerades as growth.
In other words, to become whole, the ego must first rise—claiming agency, autonomy, and identity. However, when left unbalanced, it inflates, or implodes. It forgets its context. It begins to consume rather than connect. And so the process must reverse: what inflates must deflate.
In the fiat paradigm, this inflation is literal. More is printed, and ethos is diluted. Savings decay. Meaning erodes. Value is abstracted. The economy becomes bloated with inaudible noise. And like the psyche that refuses to confront its own shadow, it begins to collapse under the weight of its own illusions.
But under Bitcoin, time is honored. Value is preserved. Energy is not abstracted but grounded.
Bitcoin is inherently deflationary—in both economic and spiritual senses. With a fixed supply, it reveals what is truly scarce. Not money, not status—but the finite number of heartbeats we each carry.
To see Bitcoin is to feel that limit in one’s soul. To hold Bitcoin is to feel Time’s weight again. To sense the importance of Bitcoin is to feel the value of preserved, potential energy. It is to confront the reality that what matters cannot be printed, inflated, or faked. In this way, Bitcoin gently confronts the ego—not through punishment, but through clarity.
Deflation, rightly understood, is not collapse—it is refinement. It strips away illusion, bloat, and excess. It restores the clarity of essence.
Spiritually, this is liberation.
The Coin of Great Price
There is an ancient parable told by a wise man:
“The kingdom of heaven is like a merchant seeking fine pearls, who, upon finding one of great price, sold all he had and bought it.”
Bitcoin is such a pearl.
But the ledger is more than a chest full of treasure. It is a key to the heart of things.
It is not just software—it is sacrament.
A symbol of what cannot be corrupted. A mirror of divine order etched into code. A map back to the sacred center.
It reflects what endures. It encodes what cannot be falsified. It remembers what we forgot: that Truth, when aligned with form, becomes Light once again.
Its design is not arbitrary. It speaks the language of life itself—
The elliptic orbits of the planets mirrored in its cryptography,
The logarithmic spiral of the nautilus shell discloses its adoption rate,
The interconnectivity of mycelium in soil reflect the network of nodes in cyberspace,
A webbed breadth of neurons across synaptic space fires with each new confirmed transaction.
It is geometry in devotion. Stillness in motion.
It is the Logos clothed in protocol.
What this key unlocks is beyond external riches. It is the eternal gold within us.
Clarity. Sovereignty. The unshakeable knowing that what is real cannot be taken. That what is sacred was never for sale.
Bitcoin is not the destination.
It is the Path.
And we—when we are willing to see it—are the Temple it leads back to.
-
 @ 727d5bb6:cce65355
2025-05-09 04:42:51
@ 727d5bb6:cce65355
2025-05-09 04:42:51VN123 là một nền tảng giải trí trực tuyến nổi bật, mang đến cho người dùng trải nghiệm thú vị và đa dạng. Với giao diện đơn giản, dễ sử dụng và tối ưu hóa cho mọi thiết bị, VN123 giúp người dùng dễ dàng tiếp cận và tham gia vào các dịch vụ giải trí yêu thích mà không gặp phải bất kỳ khó khăn nào. Nền tảng này được thiết kế với mục tiêu mang lại trải nghiệm người dùng mượt mà và không bị gián đoạn, giúp người tham gia tận hưởng những giây phút thư giãn tuyệt vời. VN123 sở hữu một giao diện thân thiện, dễ nhìn và trực quan, cho phép người dùng dễ dàng tìm kiếm các dịch vụ mà mình yêu thích. Tốc độ truy cập nhanh chóng và ổn định là một trong những yếu tố quan trọng, đảm bảo rằng mọi hoạt động của người dùng đều được diễn ra một cách suôn sẻ. Không cần lo lắng về việc mất kết nối hay gặp phải sự cố kỹ thuật, người dùng có thể hoàn toàn tập trung vào trải nghiệm giải trí của mình trên nền tảng này.
Một trong những yếu tố làm nên sự thành công của VN123 chính là tính năng bảo mật vượt trội. Nền tảng này luôn chú trọng đến việc bảo vệ thông tin cá nhân và dữ liệu của người dùng, sử dụng các công nghệ bảo mật hiện đại và hệ thống mã hóa tiên tiến. Mọi giao dịch và thông tin cá nhân của người tham gia đều được bảo vệ an toàn tuyệt đối, giúp người dùng có thể yên tâm sử dụng dịch vụ mà không phải lo lắng về việc lộ lọt dữ liệu. VN123 cam kết duy trì một môi trường trực tuyến an toàn và bảo mật, tạo ra sự tin tưởng đối với cộng đồng người dùng. Ngoài ra, nền tảng này còn có hệ thống giám sát và bảo mật chặt chẽ để ngăn chặn những hành vi gian lận hay xâm nhập trái phép. Điều này giúp duy trì tính minh bạch và công bằng cho mọi người dùng, đồng thời tạo ra một không gian giải trí an toàn và đáng tin cậy.
VN123 không chỉ chú trọng đến các yếu tố về giao diện và bảo mật, mà còn đặc biệt quan tâm đến việc nâng cao chất lượng dịch vụ khách hàng. Đội ngũ hỗ trợ của VN123 luôn sẵn sàng phục vụ và giải đáp mọi thắc mắc của người dùng 24/7. Mỗi yêu cầu hay vấn đề từ người dùng đều được đội ngũ chăm sóc khách hàng xử lý nhanh chóng và hiệu quả, giúp người tham gia có được trải nghiệm tốt nhất. Đặc biệt, VN123 luôn lắng nghe ý kiến đóng góp từ cộng đồng người dùng để liên tục cải tiến và phát triển nền tảng. Nền tảng này không ngừng nâng cấp các tính năng mới, đồng thời tổ chức các chương trình khuyến mãi và sự kiện hấp dẫn để người dùng có thể tận hưởng thêm nhiều lợi ích. Sự kết hợp giữa giao diện dễ sử dụng, bảo mật mạnh mẽ và dịch vụ khách hàng chuyên nghiệp đã giúp VN123 tạo dựng được lòng tin và sự yêu mến từ cộng đồng. Với những cải tiến liên tục và sự phát triển bền vững, VN123 đang dần trở thành một trong những nền tảng giải trí trực tuyến hàng đầu, mang đến cho người dùng những trải nghiệm tuyệt vời và thú vị.
-
 @ a5ee4475:2ca75401
2025-05-09 17:10:35
@ a5ee4475:2ca75401
2025-05-09 17:10:35Título H1 - Formatação Markdown
[Titulo com '# ' antes do texto, pode não funcionar se o título H1 for iniciado depois de um texto normal]
list #descentralismo #markdown #clients #Amethyst #Yakihonne
Título H2 [2 hashtags e espaço]
Título H3 [3 hashtags e espaço]
Título H4 [4 hashtags e espaço]
Título H5 [5 hashtags e espaço]
Título H6 [6 hashtags e espaço]
*Copie e cole o texto para enxergar os caracteres usados
Réguas horizontais
- Com 3 sublinhados (_) seguidos:
- Com 3 hífens (-) seguidos:
- Com três asteriscos (*) seguidos:
Ênfases
Negrito: - Dois asteriscos antes e depois: Este é um texto em negrito
- Dois sublinhados antes e depois: Esse é um texto em negrito
Itálico - Um asterisco antes e um depois: Esse é um texto em itálico
- Um sublinhado antes e um depois: Esse é um texto em itálico
Tachado:
~~Aqui houve uma rasura~~
Bloco de citações
Usando 1 a 3 “>”:
O bloco de citações pode ser eninhado…
…Usando cada vez mais maior-que (>).
…Mesmo com espaços entre eles.
Listas
Não-ordenadas
- Crie um tópico começando com
+,-ou*. - Subtópicos são feitos adicionando 2 espaços:
- A mudança da marcação inicial não altera a lista:
- Com asterisco
- Com sinal de mais
- Com sinal de menos
- Muito fácil!
Ordenadas
- Lorem ipsum dolor sit amet
- Consectetur adipiscing elit
- Integer molestie lorem at massa
- Você pode usar números em sequência...
- ...ou deixar tudo como
1.ou outro número.
O número inicia com recuos:
- foo
- bar
Códigos
códigona mesma linhaCaixa de código
-
Códigos intentados com 4 espaços:
// Some comments line 1 of code line 2 of code line 3 of code
-
Com 3 acentos graves antes e depois:
Marcação de texto:
Insira o texto aqui...Marcação de sintaxe:
``` js var foo = function (bar) { return bar++; };
console.log(foo(5)); ```
Tabelas
| APP | Descrição | | ------ | ----------- | | Element | App de mensagens que usa a rede Matrix. | | Simplex | App de mensagens bastante usado. | | 0xchat | App de mensagens no Nostr. |
Links
-
Link autoconvertido https://github.com/nodeca/pica (habilite o linkify para ver)
Imagens nomeadas
Minion:

Stormtroopocat:
[https://octodex.github.com/images/stormtroopocat.jpg])
Como links, imagens também tem sintaxe footnote ‘!’ + ‘Outro texto’...
[https://octodex.github.com/images/dojocat.jpg])
…com uma referência id posterior da referência na localização da URL.
Plugins
O recurso de
markdown-ité um suporte muito eficaz de plugins de sintaxe.
Emojis
*Acesse o link para entender melhor
Marcação clássica: :wink: :cry: :laughing: :yum:
Figuras Ascii (emoticons): :-) :-( 8-) ;)
Veja como mudar a exibição com o twemoji.
Sobrescrito / Subscrito
*Acesse os links para entender melhor
- 19^th^
- H~2~O
\
*Acesse o link para entender melhor
++Texto Inserido++
\
*Acesse o link para entender melhor
==Texto marcado==
Notas de Rodapé
*Acesse o link para entender melhor
Nota de rodapé 1 link[^primeiro].
Nota de rodapé 2 link[^segundo].
Rodapé^[Texto do rodapé na linha] definição na linha.
Referência duplicada no rodapé[^segundo].
[^primeiro]: Rodapé pode ter marcação
e múltiplos parágrafos.[^segundo]: Texto de rodapé.
Listas de Definição
*Acesse o link para entender melhor
Termo 1
: Definição 1 com continuação preguiçosa.
Termo 2 com marcação na linha
: Definição 2
{ algum código, parte da Definição 2 } Third paragraph of definition 2.Estilo compacto:
Termo 1 ~ Definição 1
Termo 2 ~ Definição 2a ~ Definição 2b
Esse texto é uma adaptação do:
nostr:nevent1qqsv54qfgtme38r2tl9v6ghwfj09gdjukealstkzc77mwujr56tgfwspzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtczyqy0j6zknu2lr7qrge5yt725azecflhxv6d2tzwgtwrql5llukdqjqcyqqqqqqgfdk5w3
-
 @ 57d1a264:69f1fee1
2025-05-05 05:15:02
@ 57d1a264:69f1fee1
2025-05-05 05:15:02Crabtree's Framework for Evaluating Human-Centered Research
Picture this: You've spent three weeks conducting qualitative research for a finance app redesign. You carefully recruited 12 participants, conducted in-depth interviews, and identified patterns around financial anxiety and decision paralysis. You're excited to present your findings when the inevitable happens:
"But are these results statistically significant?"
"Just 12 people? How can we make decisions that affect thousands of users based on conversations with just 12 people?"
As UX professionals, we regularly face stakeholders who evaluate our qualitative research using criteria designed for quantitative methods... This misalignment undermines the unique value qualitative research brings to product development.
Continue reading https://uxpsychology.substack.com/p/beyond-numbers-how-to-properly-evaluate
originally posted at https://stacker.news/items/971767
-
 @ 32092ec1:8e9fd13a
2025-05-09 16:13:34
@ 32092ec1:8e9fd13a
2025-05-09 16:13:34Bitcoin controversies are not new, in fact, bitcoin’s past has been riddled with one controversy after another. From the viewpoint of a financial investor, controversies are not good. They drive investor fear by amplifying uncertainty and introducing doubt about the future viability of the project. Although bitcoin is an investable asset, and there are certainly individuals, companies and countries who are investing in bitcoin strictly as a new, diversified financial asset that shows growth characteristics the likes of which humanity has rarely seen, bitcoin is not exclusively a financial instrument. Bitcoin is a network that is only as strong as the people running the miners who create the blocks, the nodes that propagate the blocks, and the users who hold the keys.
In this post I do not care to share my view on any of the latest bitcoin controversies, whether that be about OP_RETURNs, MSTR, Blackrock, MSTY, inscriptions, soft fork proposals, mempools, bitcoin strategic reserves, 21, chain surveillance, on-chain privacy, shitcoins projects, or anything else that anyone cares to opine about on Nostr or X to signal their support or opposition for what they think is critical to the success or failure of bitcoin. What I do care to share here is the ONLY winning strategy to defend bitcoin no matter what your opinion its future: USE THE TOOLS, RUN THE CODE, HOLD YOUR KEYS, TAKE RESPONSIBILITY.
In my humble opinion, the biggest problem with the current batch of bitcoin controversies is that so many people are sharing their opinions and expressing their fears about the future of bitcoin who are not even using the tools; they aren’t running the code, supporting the network or even holding their own keys. Everyone is free to share their opinions about the future of bitcoin and allowing everyone a voice is critical if we are serious about adopting the best ideas. Many visionaries have participated in the growth and development of bitcoin up to this point; we are truly standing on the shoulders of giants.
But before jumping to conclusions and spreading opinions about whether people are good faith or bad faith actors in the bitcoin space, I believe we should all hold ourselves to a certain standard. Set a minimum threshold of education for yourself before you jump on one side or the other of the latest controversy. We have tools that offer a level of sovereignty that is unparalleled in the legacy financial world, are you using them?Don’t like what MSTR is doing? Hold your keys in cold storage, then share your opinion.
Think Blackrock wants to use Bitcoin to launch a dystopian new world order agenda? Tell everyone to run a node, implement on-chain privacy strategies and hold their keys in cold storage.
Are Bitcoin developers making changes you don’t like? Use an alternative implementation, get a Bitaxe and construct your own block templates; for almost everyone this will be a stronger signal than shitposting or spreading FUD on the socials.
If you really want to defend bitcoin, think about how you are using it today. Who are you trusting to put your transactions into a block? Who are you trusting to propagate your transactions across the network? Who are you trusting to hold your keys? Who estimates your transaction fees? If you don’t trust the people who you are currently depending on, move your trust elsewhere, or increase your sovereignty and rely on yourself for some, or all, of these functions.
We make bitcoin what it is today, and we will define what bitcoin will be in the future. If we want to defend bitcoin it is our responsibility to keep it as decentralized as possible and that starts with every individual using the tools, running the code, doing the research and taking responsibility for their money.
895982
-
 @ 40b9c85f:5e61b451
2025-04-24 15:27:02
@ 40b9c85f:5e61b451
2025-04-24 15:27:02Introduction
Data Vending Machines (DVMs) have emerged as a crucial component of the Nostr ecosystem, offering specialized computational services to clients across the network. As defined in NIP-90, DVMs operate on an apparently simple principle: "data in, data out." They provide a marketplace for data processing where users request specific jobs (like text translation, content recommendation, or AI text generation)
While DVMs have gained significant traction, the current specification faces challenges that hinder widespread adoption and consistent implementation. This article explores some ideas on how we can apply the reflection pattern, a well established approach in RPC systems, to address these challenges and improve the DVM ecosystem's clarity, consistency, and usability.
The Current State of DVMs: Challenges and Limitations
The NIP-90 specification provides a broad framework for DVMs, but this flexibility has led to several issues:
1. Inconsistent Implementation
As noted by hzrd149 in "DVMs were a mistake" every DVM implementation tends to expect inputs in slightly different formats, even while ostensibly following the same specification. For example, a translation request DVM might expect an event ID in one particular format, while an LLM service could expect a "prompt" input that's not even specified in NIP-90.
2. Fragmented Specifications
The DVM specification reserves a range of event kinds (5000-6000), each meant for different types of computational jobs. While creating sub-specifications for each job type is being explored as a possible solution for clarity, in a decentralized and permissionless landscape like Nostr, relying solely on specification enforcement won't be effective for creating a healthy ecosystem. A more comprehensible approach is needed that works with, rather than against, the open nature of the protocol.
3. Ambiguous API Interfaces
There's no standardized way for clients to discover what parameters a specific DVM accepts, which are required versus optional, or what output format to expect. This creates uncertainty and forces developers to rely on documentation outside the protocol itself, if such documentation exists at all.
The Reflection Pattern: A Solution from RPC Systems
The reflection pattern in RPC systems offers a compelling solution to many of these challenges. At its core, reflection enables servers to provide metadata about their available services, methods, and data types at runtime, allowing clients to dynamically discover and interact with the server's API.
In established RPC frameworks like gRPC, reflection serves as a self-describing mechanism where services expose their interface definitions and requirements. In MCP reflection is used to expose the capabilities of the server, such as tools, resources, and prompts. Clients can learn about available capabilities without prior knowledge, and systems can adapt to changes without requiring rebuilds or redeployments. This standardized introspection creates a unified way to query service metadata, making tools like
grpcurlpossible without requiring precompiled stubs.How Reflection Could Transform the DVM Specification
By incorporating reflection principles into the DVM specification, we could create a more coherent and predictable ecosystem. DVMs already implement some sort of reflection through the use of 'nip90params', which allow clients to discover some parameters, constraints, and features of the DVMs, such as whether they accept encryption, nutzaps, etc. However, this approach could be expanded to provide more comprehensive self-description capabilities.
1. Defined Lifecycle Phases
Similar to the Model Context Protocol (MCP), DVMs could benefit from a clear lifecycle consisting of an initialization phase and an operation phase. During initialization, the client and DVM would negotiate capabilities and exchange metadata, with the DVM providing a JSON schema containing its input requirements. nip-89 (or other) announcements can be used to bootstrap the discovery and negotiation process by providing the input schema directly. Then, during the operation phase, the client would interact with the DVM according to the negotiated schema and parameters.
2. Schema-Based Interactions
Rather than relying on rigid specifications for each job type, DVMs could self-advertise their schemas. This would allow clients to understand which parameters are required versus optional, what type validation should occur for inputs, what output formats to expect, and what payment flows are supported. By internalizing the input schema of the DVMs they wish to consume, clients gain clarity on how to interact effectively.
3. Capability Negotiation
Capability negotiation would enable DVMs to advertise their supported features, such as encryption methods, payment options, or specialized functionalities. This would allow clients to adjust their interaction approach based on the specific capabilities of each DVM they encounter.
Implementation Approach
While building DVMCP, I realized that the RPC reflection pattern used there could be beneficial for constructing DVMs in general. Since DVMs already follow an RPC style for their operation, and reflection is a natural extension of this approach, it could significantly enhance and clarify the DVM specification.
A reflection enhanced DVM protocol could work as follows: 1. Discovery: Clients discover DVMs through existing NIP-89 application handlers, input schemas could also be advertised in nip-89 announcements, making the second step unnecessary. 2. Schema Request: Clients request the DVM's input schema for the specific job type they're interested in 3. Validation: Clients validate their request against the provided schema before submission 4. Operation: The job proceeds through the standard NIP-90 flow, but with clearer expectations on both sides
Parallels with Other Protocols
This approach has proven successful in other contexts. The Model Context Protocol (MCP) implements a similar lifecycle with capability negotiation during initialization, allowing any client to communicate with any server as long as they adhere to the base protocol. MCP and DVM protocols share fundamental similarities, both aim to expose and consume computational resources through a JSON-RPC-like interface, albeit with specific differences.
gRPC's reflection service similarly allows clients to discover service definitions at runtime, enabling generic tools to work with any gRPC service without prior knowledge. In the REST API world, OpenAPI/Swagger specifications document interfaces in a way that makes them discoverable and testable.
DVMs would benefit from adopting these patterns while maintaining the decentralized, permissionless nature of Nostr.
Conclusion
I am not attempting to rewrite the DVM specification; rather, explore some ideas that could help the ecosystem improve incrementally, reducing fragmentation and making the ecosystem more comprehensible. By allowing DVMs to self describe their interfaces, we could maintain the flexibility that makes Nostr powerful while providing the structure needed for interoperability.
For developers building DVM clients or libraries, this approach would simplify consumption by providing clear expectations about inputs and outputs. For DVM operators, it would establish a standard way to communicate their service's requirements without relying on external documentation.
I am currently developing DVMCP following these patterns. Of course, DVMs and MCP servers have different details; MCP includes capabilities such as tools, resources, and prompts on the server side, as well as 'roots' and 'sampling' on the client side, creating a bidirectional way to consume capabilities. In contrast, DVMs typically function similarly to MCP tools, where you call a DVM with an input and receive an output, with each job type representing a different categorization of the work performed.
Without further ado, I hope this article has provided some insight into the potential benefits of applying the reflection pattern to the DVM specification.
-
 @ c631e267:c2b78d3e
2025-05-02 20:05:22
@ c631e267:c2b78d3e
2025-05-02 20:05:22Du bist recht appetitlich oben anzuschauen, \ doch unten hin die Bestie macht mir Grauen. \ Johann Wolfgang von Goethe
Wie wenig bekömmlich sogenannte «Ultra-Processed Foods» wie Fertiggerichte, abgepackte Snacks oder Softdrinks sind, hat kürzlich eine neue Studie untersucht. Derweil kann Fleisch auch wegen des Einsatzes antimikrobieller Mittel in der Massentierhaltung ein Problem darstellen. Internationale Bemühungen, diesen Gebrauch zu reduzieren, um die Antibiotikaresistenz bei Menschen einzudämmen, sind nun möglicherweise gefährdet.
Leider ist Politik oft mindestens genauso unappetitlich und ungesund wie diverse Lebensmittel. Die «Corona-Zeit» und ihre Auswirkungen sind ein beredtes Beispiel. Der Thüringer Landtag diskutiert gerade den Entwurf eines «Coronamaßnahmen-Unrechtsbereinigungsgesetzes» und das kanadische Gesundheitsministerium versucht, tausende Entschädigungsanträge wegen Impfnebenwirkungen mit dem Budget von 75 Millionen Dollar unter einen Hut zu bekommen. In den USA soll die Zulassung von Covid-«Impfstoffen» überdacht werden, während man sich mit China um die Herkunft des Virus streitet.
Wo Corona-Verbrecher von Medien und Justiz gedeckt werden, verfolgt man Aufklärer und Aufdecker mit aller Härte. Der Anwalt und Mitbegründer des Corona-Ausschusses Reiner Fuellmich, der seit Oktober 2023 in Untersuchungshaft sitzt, wurde letzte Woche zu drei Jahren und neun Monaten verurteilt – wegen Veruntreuung. Am Mittwoch teilte der von vielen Impfschadensprozessen bekannte Anwalt Tobias Ulbrich mit, dass er vom Staatsschutz verfolgt wird und sich daher künftig nicht mehr öffentlich äußern werde.
Von der kommenden deutschen Bundesregierung aus Wählerbetrügern, Transatlantikern, Corona-Hardlinern und Russenhassern kann unmöglich eine Verbesserung erwartet werden. Nina Warken beispielsweise, die das Ressort Gesundheit übernehmen soll, diffamierte Maßnahmenkritiker als «Coronaleugner» und forderte eine Impfpflicht, da die wundersamen Injektionen angeblich «nachweislich helfen». Laut dem designierten Außenminister Johann Wadephul wird Russland «für uns immer der Feind» bleiben. Deswegen will er die Ukraine «nicht verlieren lassen» und sieht die Bevölkerung hinter sich, solange nicht deutsche Soldaten dort sterben könnten.
Eine wichtige Personalie ist auch die des künftigen Regierungssprechers. Wenngleich Hebestreit an Arroganz schwer zu überbieten sein wird, dürfte sich die Art der Kommunikation mit Stefan Kornelius in der Sache kaum ändern. Der Politikchef der Süddeutschen Zeitung «prägte den Meinungsjournalismus der SZ» und schrieb «in dieser Rolle auch für die Titel der Tamedia». Allerdings ist, anders als noch vor zehn Jahren, die Einbindung von Journalisten in Thinktanks wie die Deutsche Atlantische Gesellschaft (DAG) ja heute eher eine Empfehlung als ein Problem.
Ungesund ist definitiv auch die totale Digitalisierung, nicht nur im Gesundheitswesen. Lauterbachs Abschiedsgeschenk, die «abgesicherte» elektronische Patientenakte (ePA) ist völlig überraschenderweise direkt nach dem Bundesstart erneut gehackt worden. Norbert Häring kommentiert angesichts der Datenlecks, wer die ePA nicht abwähle, könne seine Gesundheitsdaten ebensogut auf Facebook posten.
Dass die staatlichen Kontrolleure so wenig auf freie Software und dezentrale Lösungen setzen, verdeutlicht die eigentlichen Intentionen hinter der Digitalisierungswut. Um Sicherheit und Souveränität geht es ihnen jedenfalls nicht – sonst gäbe es zum Beispiel mehr Unterstützung für Bitcoin und für Initiativen wie die der Spar-Supermärkte in der Schweiz.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 33c84388:ab6c6bdb
2025-05-09 04:25:30
@ 33c84388:ab6c6bdb
2025-05-09 04:25:30Se você está em busca de uma plataforma de jogos online emocionante, que ofereça uma grande variedade de opções, recursos inovadores e uma experiência do usuário sem igual, a 358Bet é a escolha ideal. Esta plataforma se destaca no competitivo mundo do entretenimento online ao proporcionar uma experiência envolvente e fluida para os jogadores de todo o Brasil. Se você é um jogador experiente ou está apenas começando, a 358Bet oferece algo para todos. Neste artigo, vamos apresentar a 358Bet, destacar alguns dos jogos mais populares da plataforma e discutir a experiência do jogador que a torna um dos destinos mais procurados no universo do entretenimento online.
Introdução à Plataforma: Uma Experiência Robusta e Intuitiva A 358Bet foi desenvolvida para proporcionar aos usuários uma interface simples e intuitiva, que garante uma experiência de navegação tranquila. O layout da plataforma é limpo, organizado e fácil de usar, tornando-a acessível até mesmo para iniciantes. Se você está explorando os jogos, verificando as promoções ou gerenciando sua conta, o site oferece uma jornada sem esforço. A versão móvel da 358beté igualmente impressionante, permitindo que os jogadores desfrutem de seus jogos favoritos a qualquer momento e em qualquer lugar, garantindo que você tenha tudo na ponta dos dedos.
A plataforma também utiliza tecnologias avançadas para garantir que sua experiência seja segura, rápida e confiável. Com o uso de tecnologias de criptografia de última geração, os jogadores podem confiar que suas informações pessoais e financeiras estão sempre protegidas. Esse foco em segurança torna a 358Bet uma plataforma confiável para quem valoriza a privacidade e a proteção de dados.
Além disso, a plataforma é otimizada para oferecer um desempenho excelente, com tempos de carregamento rápidos e mínima possibilidade de quedas. Se você está jogando jogos ao vivo ou explorando novos títulos, certamente apreciará a jogabilidade fluida e responsiva, o que agrega ainda mais qualidade à sua experiência.
Introdução aos Jogos: Uma Seleção Diversificada para Todos os Gostos Um dos principais destaques da 358Bet é sua vasta coleção de jogos. Desde emocionantes jogos de mesa até opções de dealers ao vivo, há sempre algo excitante para jogar. A plataforma oferece uma variedade de jogos de alta qualidade, para agradar a todos os gostos e preferências.
-
Jogos de Slot: Se você gosta de girar os rolos, encontrará uma ampla gama de jogos de slot com diferentes temas, recursos e pagamentos. Desde os slots clássicos até os lançamentos mais modernos, a 358Bet oferece uma seleção diversificada para satisfazer as necessidades de todos os jogadores. Os jogos possuem gráficos impressionantes, trilhas sonoras imersivas e recursos bônus inovadores, tornando cada giro uma aventura emocionante.
-
Jogos de Mesa: Para aqueles que preferem jogos de mais estratégia e habilidade, a 358Bet oferece uma variedade de jogos de mesa, como blackjack, bacará e roleta. Esses jogos oferecem uma experiência clássica com toques modernos, sendo perfeitos para jogadores que buscam tanto diversão casual quanto ação competitiva.
-
Jogos com Dealers Ao Vivo: Se você está buscando uma experiência mais interativa e imersiva, os jogos com dealers ao vivo da 358Bet certamente irão impressionar. Com dealers profissionais, transmissões ao vivo e a oportunidade de interagir com outros jogadores, os jogos ao vivo proporcionam uma experiência que se aproxima muito de um ambiente de jogo físico. Jogadores podem desfrutar de títulos como blackjack e roleta em tempo real, aumentando a excitação do jogo.
-
Esportes Virtuais e Jogos Especiais: Para algo um pouco diferente, a 358Bet também oferece esportes virtuais e jogos especiais. Esses jogos oferecem uma visão única sobre experiências tradicionais de entretenimento, permitindo que os jogadores se envolvam com eventos esportivos virtuais ou testem suas habilidades em desafios rápidos e emocionantes.
Conclusão: Por Que Escolher a 358Bet? A 358Bet é muito mais do que apenas uma plataforma de jogos online; é uma experiência completa de entretenimento. Com uma grande variedade de jogos, uma interface segura e amigável, e um foco incansável na satisfação do jogador, está claro por que tantos optam por essa plataforma. Se você está jogando para se divertir ou buscando grandes vitórias, a 358Bet oferece tudo o que você precisa para uma jornada de jogo envolvente e recompensadora. Com desempenho ágil, uma seleção diversificada de jogos e compromisso com o jogo responsável, a 358Bet é um dos principais destinos para os jogadores no Brasil que buscam melhorar sua experiência de entretenimento online.
-
-
 @ 2e8970de:63345c7a
2025-05-10 11:08:31
@ 2e8970de:63345c7a
2025-05-10 11:08:31
What gear are you using? Any new/used stuff you are currently trying to buy/sell?
originally posted at https://stacker.news/items/976340
-
 @ c9badfea:610f861a
2025-05-09 15:32:59
@ c9badfea:610f861a
2025-05-09 15:32:59- Install Feeder (it's free and open source)
- Discover RSS feeds from various sources (see links below)
- Copy the Feed URL
- Open Feeder, tap the ⁞ icon, and choose Add Feed
- Paste the Feed URL and tap Search
- Select the found RSS feed item
- Scroll down and tap OK
Some Sources
ℹ️ You can also use YouTube channel URLs as feeds
-
 @ 6e64b83c:94102ee8
2025-04-23 20:23:34
@ 6e64b83c:94102ee8
2025-04-23 20:23:34How to Run Your Own Nostr Relay on Android with Cloudflare Domain
Prerequisites
- Install Citrine on your Android device:
- Visit https://github.com/greenart7c3/Citrine/releases
- Download the latest release using:
- zap.store
- Obtainium
- F-Droid
- Or download the APK directly
-
Note: You may need to enable "Install from Unknown Sources" in your Android settings
-
Domain Requirements:
- Purchase a domain if you don't have one
-
Transfer your domain to Cloudflare if it's not already there (for free SSL certificates and cloudflared support)
-
Tools to use:
- nak (the nostr army knife):
- Download from https://github.com/fiatjaf/nak/releases
- Installation steps:
-
For Linux/macOS: ```bash # Download the appropriate version for your system wget https://github.com/fiatjaf/nak/releases/latest/download/nak-linux-amd64 # for Linux # or wget https://github.com/fiatjaf/nak/releases/latest/download/nak-darwin-amd64 # for macOS
# Make it executable chmod +x nak-*
# Move to a directory in your PATH sudo mv nak-* /usr/local/bin/nak
- For Windows:batch # Download the Windows version curl -L -o nak.exe https://github.com/fiatjaf/nak/releases/latest/download/nak-windows-amd64.exe# Move to a directory in your PATH (e.g., C:\Windows) move nak.exe C:\Windows\nak.exe
- Verify installation:bash nak --version ```
Setting Up Citrine
- Open the Citrine app
- Start the server
- You'll see it running on
ws://127.0.0.1:4869(local network only) - Go to settings and paste your npub into "Accept events signed by" inbox and press the + button. This prevents others from publishing events to your personal relay.
Installing Required Tools
- Install Termux from Google Play Store
- Open Termux and run:
bash pkg update && pkg install wget wget https://github.com/cloudflare/cloudflared/releases/latest/download/cloudflared-linux-arm64.deb dpkg -i cloudflared-linux-arm64.debCloudflare Authentication
- Run the authentication command:
bash cloudflared tunnel login - Follow the instructions:
- Copy the provided URL to your browser
- Log in to your Cloudflare account
- If the URL expires, copy it again after logging in
Creating the Tunnel
- Create a new tunnel:
bash cloudflared tunnel create <TUNNEL_NAME> - Choose any name you prefer for your tunnel
-
Copy the tunnel ID after creating the tunnel
-
Create and configure the tunnel config:
bash touch ~/.cloudflared/config.yml nano ~/.cloudflared/config.yml -
Add this configuration (replace the placeholders with your values): ```yaml tunnel:
credentials-file: /data/data/com.termux/files/home/.cloudflared/ .json ingress: - hostname: nostr.yourdomain.com service: ws://localhost:4869
- service: http_status:404 ```
- Note: In nano editor:
CTRL+Oand Enter to saveCTRL+Xto exit
-
Note: Check the credentials file path in the logs
-
Validate your configuration:
bash cloudflared tunnel validate -
Start the tunnel:
bash cloudflared tunnel run my-relay
Preventing Android from Killing the Tunnel
Run these commands to maintain tunnel stability:
bash date && apt install termux-tools && termux-setup-storage && termux-wake-lock echo "nameserver 1.1.1.1" > $PREFIX/etc/resolv.confTip: You can open multiple Termux sessions by swiping from the left edge of the screen while keeping your tunnel process running.
Updating Your Outbox Model Relays
Once your relay is running and accessible via your domain, you'll want to update your relay list in the Nostr network. This ensures other clients know about your relay and can connect to it.
Decoding npub (Public Key)
Private keys (nsec) and public keys (npub) are encoded in bech32 format, which includes: - A prefix (like nsec1, npub1 etc.) - The encoded data - A checksum
This format makes keys: - Easy to distinguish - Hard to copy incorrectly
However, most tools require these keys in hexadecimal (hex) format.
To decode an npub string to its hex format:
bash nak decode nostr:npub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4Change it with your own npub.
bash { "pubkey": "6e64b83c1f674fb00a5f19816c297b6414bf67f015894e04dd4c657e94102ee8" }Copy the pubkey value in quotes.
Create a kind 10002 event with your relay list:
- Include your new relay with write permissions
- Include other relays you want to read from and write to, omit 3rd parameter to make it both read and write
Example format:
json { "kind": 10002, "tags": [ ["r", "wss://your-relay-domain.com", "write"], ["r", "wss://eden.nostr.land/"], ["r", "wss://nos.lol/"], ["r", "wss://nostr.bitcoiner.social/"], ["r", "wss://nostr.mom/"], ["r", "wss://relay.primal.net/"], ["r", "wss://nostr.wine/", "read"], ["r", "wss://relay.damus.io/"], ["r", "wss://relay.nostr.band/"], ["r", "wss://relay.snort.social/"] ], "content": "" }Save it to a file called
event.jsonNote: Add or remove any relays you want. To check your existing 10002 relays: - Visit https://nostr.band/?q=by%3Anpub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4+++kind%3A10002 - nostr.band is an indexing service, it probably has your relay list. - Replace
npub1xxxin the URL with your own npub - Click "VIEW JSON" from the menu to see the raw event - Or use thenaktool if you know the relaysbash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.comReplace `<your-pubkey>` with your public key in hex format (you can get it using `nak decode <your-npub>`)- Sign and publish the event:
- Use a Nostr client that supports kind 10002 events
- Or use the
nakcommand-line tool:bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)
Important Security Notes: 1. Never share your nsec (private key) with anyone 2. Consider using NIP-49 encrypted keys for better security 3. Never paste your nsec or private key into the terminal. The command will be saved in your shell history, exposing your private key. To clear the command history: - For bash: use
history -c- For zsh: usefc -Wto write history to file, thenfc -pto read it back - Or manually edit your shell history file (e.g.,~/.zsh_historyor~/.bash_history) 4. if you're usingzsh, usefc -pto prevent the next command from being saved to history 5. Or temporarily disable history before running sensitive commands:bash unset HISTFILE nak key encrypt ... set HISTFILEHow to securely create NIP-49 encypted private key
```bash
Read your private key (input will be hidden)
read -s SECRET
Read your password (input will be hidden)
read -s PASSWORD
encrypt command
echo "$SECRET" | nak key encrypt "$PASSWORD"
copy and paste the ncryptsec1 text from the output
read -s ENCRYPTED nak key decrypt "$ENCRYPTED"
clear variables from memory
unset SECRET PASSWORD ENCRYPTED ```
On a Windows command line, to read from stdin and use the variables in
nakcommands, you can use a combination ofset /pto read input and then use those variables in your command. Here's an example:```bash @echo off set /p "SECRET=Enter your secret key: " set /p "PASSWORD=Enter your password: "
echo %SECRET%| nak key encrypt %PASSWORD%
:: Clear the sensitive variables set "SECRET=" set "PASSWORD=" ```
If your key starts with
ncryptsec1, thenaktool will securely prompt you for a password when using the--secparameter, unless the command is used with a pipe< >or|.bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)- Verify the event was published:
- Check if your relay list is visible on other relays
-
Use the
naktool to fetch your kind 10002 events:bash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.com -
Testing your relay:
- Try connecting to your relay using different Nostr clients
- Verify you can both read from and write to your relay
- Check if events are being properly stored and retrieved
- Tip: Use multiple Nostr clients to test different aspects of your relay
Note: If anyone in the community has a more efficient method of doing things like updating outbox relays, please share your insights in the comments. Your expertise would be greatly appreciated!
-
 @ 33c84388:ab6c6bdb
2025-05-09 04:22:06
@ 33c84388:ab6c6bdb
2025-05-09 04:22:06A plataforma 944Bet é uma das mais inovadoras opções para quem procura uma experiência de entretenimento online emocionante e segura. Com uma ampla gama de jogos e uma interface amigável, ela se destaca entre outras plataformas e promete proporcionar diversão e recompensas para seus usuários.
Plataforma de Apostas e Jogos de Alta Qualidade O 944Bet foi criado com o objetivo de oferecer uma experiência de usuário única, centrada em jogabilidade fluida e recursos tecnológicos avançados. O site tem uma navegação simples, permitindo que os jogadores se conectem rapidamente e com facilidade, independentemente do dispositivo utilizado, seja desktop ou dispositivos móveis. A plataforma também oferece suporte em português, garantindo que os usuários brasileiros tenham uma experiência personalizada e tranquila.
A interface do 944Bet é limpa e intuitiva, com menus e categorias de jogos bem organizados. Além disso, o design é moderno, com gráficos de alta qualidade que atraem os jogadores e criam um ambiente visualmente agradável. Com uma estrutura confiável e segura, o site assegura que todos os dados pessoais e transações financeiras sejam protegidos, proporcionando tranquilidade para os jogadores.
Variedade de Jogos para Todos os Gostos O 944Bet se destaca pela variedade de opções de entretenimento que oferece aos seus jogadores. Desde jogos de mesa, como blackjack e roleta, até opções mais inovadoras, como slots e títulos de jogos de arcade, a plataforma oferece algo para todos os gostos. Além disso, há uma extensa seleção de esportes virtuais, com eventos e competições simuladas que capturam a atenção de quem gosta de desafios rápidos e emocionantes.
Os jogos disponíveis são atualizados regularmente, garantindo que os jogadores sempre tenham algo novo para explorar. As opções são escolhidas com base na popularidade, no entretenimento e na qualidade da jogabilidade. A plataforma também está em constante evolução, com novos títulos sendo adicionados frequentemente, para que a experiência do usuário nunca se torne monótona.
A Experiência do Jogador no 944Bet A experiência do jogador é uma das prioridades do 944Bet, que se esforça para oferecer uma jornada divertida, envolvente e cheia de oportunidades para ganhar. O processo de inscrição é simples, rápido e descomplicado, permitindo que novos usuários se registrem e comecem a jogar em poucos minutos. O suporte ao cliente é outro ponto forte, com uma equipe dedicada e pronta para ajudar os jogadores em qualquer dúvida ou problema que possa surgir.
Para garantir que os jogadores tenham uma experiência ainda mais rica, o 944Bet oferece uma série de promoções e bônus que incentivam a participação ativa na plataforma. Desde bônus de boas-vindas até ofertas de recarga, os jogadores têm várias oportunidades de aumentar suas chances de ganhar. Essas promoções são oferecidas de forma transparente, permitindo que os jogadores saibam exatamente o que estão recebendo.
Além disso, a plataforma conta com um sistema de pagamento rápido e eficiente, facilitando os depósitos e retiradas de forma simples e sem complicações. As transações são processadas de maneira ágil, e a plataforma aceita uma grande variedade de métodos de pagamento, incluindo cartões de crédito, carteiras digitais e transferências bancárias.
Conclusão O 944Bet é uma plataforma que oferece mais do que apenas jogos de qualidade; ela proporciona uma experiência completa, com uma interface fácil de usar, uma variedade impressionante de opções de entretenimento e um compromisso constante com a segurança e a satisfação do jogador. Se você está em busca de uma nova plataforma para testar suas habilidades e desfrutar de uma experiência divertida, o 944Bet é, sem dúvida, uma excelente escolha. Com recursos que atendem a todos os perfis de jogadores e promoções atrativas, esta plataforma está pronta para se tornar a favorita dos brasileiros.
-
 @ c631e267:c2b78d3e
2025-04-25 20:06:24
@ c631e267:c2b78d3e
2025-04-25 20:06:24Die Wahrheit verletzt tiefer als jede Beleidigung. \ Marquis de Sade
Sagen Sie niemals «Terroristin B.», «Schwachkopf H.», «korrupter Drecksack S.» oder «Meinungsfreiheitshasserin F.» und verkneifen Sie sich Memes, denn so etwas könnte Ihnen als Beleidigung oder Verleumdung ausgelegt werden und rechtliche Konsequenzen haben. Auch mit einer Frau M.-A. S.-Z. ist in dieser Beziehung nicht zu spaßen, sie gehört zu den Top-Anzeigenstellern.
«Politikerbeleidigung» als Straftatbestand wurde 2021 im Kampf gegen «Rechtsextremismus und Hasskriminalität» in Deutschland eingeführt, damals noch unter der Regierung Merkel. Im Gesetz nicht festgehalten ist die Unterscheidung zwischen schlechter Hetze und guter Hetze – trotzdem ist das gängige Praxis, wie der Titel fast schon nahelegt.
So dürfen Sie als Politikerin heute den Tesla als «Nazi-Auto» bezeichnen und dies ausdrücklich auf den Firmengründer Elon Musk und dessen «rechtsextreme Positionen» beziehen, welche Sie nicht einmal belegen müssen. [1] Vielleicht ernten Sie Proteste, jedoch vorrangig wegen der «gut bezahlten, unbefristeten Arbeitsplätze» in Brandenburg. Ihren Tweet hat die Berliner Senatorin Cansel Kiziltepe inzwischen offenbar dennoch gelöscht.
Dass es um die Meinungs- und Pressefreiheit in der Bundesrepublik nicht mehr allzu gut bestellt ist, befürchtet man inzwischen auch schon im Ausland. Der Fall des Journalisten David Bendels, der kürzlich wegen eines Faeser-Memes zu sieben Monaten Haft auf Bewährung verurteilt wurde, führte in diversen Medien zu Empörung. Die Welt versteckte ihre Kritik mit dem Titel «Ein Urteil wie aus einer Diktatur» hinter einer Bezahlschranke.
Unschöne, heutzutage vielleicht strafbare Kommentare würden mir auch zu einigen anderen Themen und Akteuren einfallen. Ein Kandidat wäre der deutsche Bundesgesundheitsminister (ja, er ist es tatsächlich immer noch). Während sich in den USA auf dem Gebiet etwas bewegt und zum Beispiel Robert F. Kennedy Jr. will, dass die Gesundheitsbehörde (CDC) keine Covid-Impfungen für Kinder mehr empfiehlt, möchte Karl Lauterbach vor allem das Corona-Lügengebäude vor dem Einsturz bewahren.
«Ich habe nie geglaubt, dass die Impfungen nebenwirkungsfrei sind», sagte Lauterbach jüngst der ZDF-Journalistin Sarah Tacke. Das steht in krassem Widerspruch zu seiner früher verbreiteten Behauptung, die Gen-Injektionen hätten keine Nebenwirkungen. Damit entlarvt er sich selbst als Lügner. Die Bezeichnung ist absolut berechtigt, dieser Mann dürfte keinerlei politische Verantwortung tragen und das Verhalten verlangt nach einer rechtlichen Überprüfung. Leider ist ja die Justiz anderweitig beschäftigt und hat außerdem selbst keine weiße Weste.
Obendrein kämpfte der Herr Minister für eine allgemeine Impfpflicht. Er beschwor dabei das Schließen einer «Impflücke», wie es die Weltgesundheitsorganisation – die «wegen Trump» in finanziellen Schwierigkeiten steckt – bis heute tut. Die WHO lässt aktuell ihre «Europäische Impfwoche» propagieren, bei der interessanterweise von Covid nicht mehr groß die Rede ist.
Einen «Klima-Leugner» würden manche wohl Nir Shaviv nennen, das ist ja nicht strafbar. Der Astrophysiker weist nämlich die Behauptung von einer Klimakrise zurück. Gemäß seiner Forschung ist mindestens die Hälfte der Erderwärmung nicht auf menschliche Emissionen, sondern auf Veränderungen im Sonnenverhalten zurückzuführen.
Das passt vielleicht auch den «Klima-Hysterikern» der britischen Regierung ins Konzept, die gerade Experimente zur Verdunkelung der Sonne angekündigt haben. Produzenten von Kunstfleisch oder Betreiber von Insektenfarmen würden dagegen vermutlich die Geschichte vom fatalen CO2 bevorzugen. Ihnen würde es besser passen, wenn der verantwortungsvolle Erdenbürger sein Verhalten gründlich ändern müsste.
In unserer völlig verkehrten Welt, in der praktisch jede Verlautbarung außerhalb der abgesegneten Narrative potenziell strafbar sein kann, gehört fast schon Mut dazu, Dinge offen anzusprechen. Im «besten Deutschland aller Zeiten» glaubten letztes Jahr nur noch 40 Prozent der Menschen, ihre Meinung frei äußern zu können. Das ist ein Armutszeugnis, und es sieht nicht gerade nach Besserung aus. Umso wichtiger ist es, dagegen anzugehen.
[Titelbild: Pixabay]
--- Quellen: ---
[1] Zur Orientierung wenigstens ein paar Hinweise zur NS-Vergangenheit deutscher Automobilhersteller:
- Volkswagen
- Porsche
- Daimler-Benz
- BMW
- Audi
- Opel
- Heute: «Auto-Werke für die Rüstung? Rheinmetall prüft Übernahmen»
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 3eba5ef4:751f23ae
2025-05-09 01:52:16
@ 3eba5ef4:751f23ae
2025-05-09 01:52:16Crypto Insights
Proposal to Remove OP_RETURN Limit Sparks Heated Debate Among Developers
Introduced in 2014, OP_RETURN allows small pieces of data—like timestamps or short messages—to be included in Bitcoin transactions, serving as a lightweight method to store limited information on-chain. Over time, the size limit was reduced to prevent spam, before settling at the current 83 byte-limit.
Peter Todd recently proposed removing the limit entirely. He argues that the restriction fails to deter misuse and instead complicates things, as it pushes developers to use workarounds—like
scriptsigor unspendable outputs (such as storing data in unspendable Taproot outputs)—to embed media, spam, or arbitrary data, which bloats the UTXO set.Pieter Wuille, who also supports lifting the OP_RETURN cap, points out that standardness policies can’t truly stop well-funded entities from broadcasting data-heavy transactions directly to miners. The network is strong and block space is always full—even without spam, so those rules are no longer as useful.
In short, those in favor of removing the OP_RETURN limit argue that the restriction is futile, and that alternative data storage methods within blocks already exist in abundance.
On the other side, opponents believe the limit must stay, as using OP_RETURN to store arbitrary data violates Satoshi’s intent and Bitcoin’s purpose as a financial network (Luke Dashjr). Other opposing voices include:
- @Mechanic from Ocean Mining: The devs just instinctively knew, you don’t use Bitcoin for arbitrary file storage and you do everything you can to make Bitcoin awkward to use for that purpose.
- Jason Hughes: Bitcoin Core developers are about to merge a change that turns Bitcoin into a worthless altcoin…
Here for more perspectives on this debate.
Comparing Three Cluster Linearization Techniques
Pieter Wuille compares three cluster linearization strategies—SFL (spanning-forest linearization), GGT, and CSS (candidate set search)—and follows up with benchmark results for each.
StarkWare Introduces ColliderVM: A BitVM Alternative for Computation and L2 Bridges
ColliderVM protocol is StarkWare’s research effort on a BitVM alternative. It retains the same trust assumptions but without needing fraud proofs, thus eliminating fraud-proof time window. Researchers use ColliderVM to sketch a trustless bridge design to a L2 network, aiming to scale Bitcoin with a rollup-like design and enabling more functionality and privacy.
The paper: ColliderVM: Stateful Computation on Bitcoin without Fraud Proofs
And a talk: Bitcoin Horizons: from OP_CAT to Covenants
Bitcoin Goes Green(ish): Over 50% of Mining Now Uses Sustainable Energy
A report from the Cambridge Centre for Alternative Finance (CCAF) finds that 52.4% of Bitcoin mining now uses green energy. Of that, 42.6% comes from renewables such as hydro and wind, while 9.8% comes from nuclear.
Top Reads on Blockchain and Beyond
Kraken Shares Lessons on Identifying a North Korean Hacker in Job Recruitment
Kraken recently uncovered a North Korean hacker attempting to apply for a job. They’ve shared insights on how to detect and prevent such actors at various stages of the hiring process.
Round-Efficient Adaptively Secure Threshold Signatures with Rewinding
A threshold signature scheme allows distributing a signing key to n users, such that any t of them can jointly sign, but any t−1 cannot. It is desirable to prove adaptive security of threshold signature schemes, which considers adversaries that can adaptively corrupt honest users even after interacting with them. For a class of signatures that relies on security proofs with rewinding, such as Schnorr signatures, proving adaptive security entails significant challenges. This work proposes two threshold signature schemes that are provably adaptively secure with rewinding proofs. Our proofs are solely in the random oracle model (ROM), without relying on the algebraic group model (AGM).
Read the full paper.
Vitalik on Simplifying Ethereum L1, Taking Cues from Bitcoin’s Minimalism
In a new post titled Simplifying the L1, Vitalik suggests simplifying Ethereum’s base layer by moving from EVM to RISC-V (or another minimal VM), adopting Simple Serialize, and embracing Tinygrad’s coding philosophy.
Key impacts of this shift include:
- Radical efficiency improvements: Contracts can run directly in ZK provers without interpreter overhead. According to Succinct, performance could increase by over 100x in many cases.
- Radically improved simplicity: RISC-V spec is far more minimal than the EVM. Other options like Cairo also offer a simple design.
- All the benefits that motivated Ethereum Object Format (EOF): Including code sections, friendly static analysis, and larger code size limits.
- Expanded tooling: Solidity and Vyper can target the new VM with backend updates. If RISC-V is chosen, developers may be able to port existing code from mainstream languages.
- Reduced reliance on precompiles: Most precompiles may become obsolete—except perhaps highly optimized elliptic curve operations, which could also be phased out with advances in quantum computing.
-
 @ d41bf82f:ed90d888
2025-05-10 08:09:15
@ d41bf82f:ed90d888
2025-05-10 08:09:15บทที่ 3: ตะวันออกแห่งเอเดน (East of Eden)
บทนี้เจาะลึกต้นกำเนิดของโครงสร้างอำนาจในมนุษยชาติผ่านมุมมองเชิงประวัติศาสตร์และเศรษฐศาสตร์ โดยเฉพาะการเปลี่ยนแปลงครั้งสำคัญที่เรียกว่า การปฏิวัติเกษตรกรรม ซึ่งพลิกโฉมวิถีชีวิตมนุษย์จากการเป็นนักล่าสัตว์และเก็บของป่า มาสู่สังคมที่ตั้งถิ่นฐานถาวร สะสมทรัพย์สิน และมีแนวโน้มที่จะใช้ความรุนแรงและจัดองค์กรทางอำนาจที่ซับซ้อนมากขึ้น
การเปลี่ยนผ่านดังกล่าวสามารถเห็นภาพได้อย่างคมชัดผ่านสัญลักษณ์ในพระคัมภีร์ไบเบิล จากเรื่องราวของคาอินและอาเบล:
“และพระเจ้าตรัสกับคาอินว่า ‘อาเบล น้องชายของเจ้าอยู่ที่ไหน?’ คาอินตอบว่า ‘ข้าพระองค์ไม่ทราบ ข้าพระองค์เป็นผู้ดูแลน้องชายของข้าหรือ?’ พระเจ้าตรัสว่า ‘เจ้าทำอะไรลงไป? เสียงเลือดของน้องชายเจ้าร้องต่อเรามาจากพื้นดิน’” (ปฐมกาล 4:9-10)
นี่ไม่ใช่เพียงบทสนทนาทางศาสนา แต่สามารถตีความในเชิงสัญลักษณ์ว่าเป็นการบันทึกครั้งแรกของอาชญากรรมที่เกิดจากตรรกะของการเป็นเจ้าของและความรุนแรง คาอิน ผู้เป็น “ชาวนา” ได้สังหารน้องชายของตนเองจากแรงริษยาและการแข่งขันในบริบทของการถวายผลผลิต ความเปรียบเปรยนี้สะท้อนถึงความเปลี่ยนแปลงของตรรกะทางสังคมเมื่อมนุษย์เข้าสู่ยุคเกษตรกรรม
ในยุคก่อนเกษตรกรรม มนุษย์อยู่กันเป็นกลุ่มเล็ก ๆ พึ่งพาทรัพยากรธรรมชาติในพื้นที่กว้าง ไม่มีแรงจูงใจจะใช้ความรุนแรง เพราะไม่มีทรัพย์สินให้แย่งชิง อาหารต้องบริโภคทันที ไม่มีการสะสม ทำให้ไม่มีใครร่ำรวยหรือยากจนอย่างชัดเจน โครงสร้างสังคมจึงเท่าเทียมและร่วมมือกันได้ดี
แต่เมื่อมนุษย์เริ่มเพาะปลูกและเลี้ยงสัตว์ พื้นที่การผลิตอาหารต้องได้รับการดูแลต่อเนื่อง ทำให้ไม่สามารถอพยพหนีภัยได้ง่าย และเมื่อมีผลผลิตมากขึ้น ก็ยิ่งเป็นเป้าหมายของการปล้นสะดม ส่งผลให้กลุ่มนักรบผู้ใช้ความรุนแรงสามารถสะสมทรัพยากรและอำนาจได้มากขึ้น และบางกลุ่มก็พัฒนาเป็นรัฐ ระบบการป้องกันและการเก็บส่วยในรูปแบบของรัฐจึงค่อยๆ ก่อตัวขึ้นจากพันธมิตรระหว่างนักรบกับนักบวช
ทรัพย์สิน ส่วนตัวซึ่งไม่เคยมีความสำคัญในสังคมนักล่าสัตว์ กลายเป็นสิ่งที่จำเป็นในสังคมเกษตรกรรม เพราะไม่มีใครจะเพาะปลูกด้วยแรงงานของตนเองหากรู้ว่าจะถูกปล้นไป ความชัดเจนของกรรมสิทธิ์จึงเป็นสิ่งจำเป็น แต่ขณะเดียวกัน กลไกของความรุนแรงก็ทำให้สิทธิในทรัพย์สินตกอยู่ในความเสี่ยง ระบบของรัฐในยุคแรกจึงเป็นการผูกขาดความรุนแรงในนามของความคุ้มครอง
ในสังคมเกษตรกรรมที่ผลิตภาพต่ำ ผู้คนจำนวนมากต้องพึ่งพารูปแบบการป้องกันทางเศรษฐกิจที่เรียกว่า “หมู่บ้านปิด” ซึ่งความเสี่ยงถูกกระจายระหว่างเจ้าของที่ดินกับชาวนา โดยมีหัวหน้าหมู่บ้านเป็นตัวกลางในความสัมพันธ์ทางเศรษฐกิจ การจ่ายค่าเช่าที่ดินในรูปแบบผลผลิตแทนเงิน ช่วยให้เจ้าของที่ดินและผู้เช่าสามารถรับมือกับภัยพิบัติร่วมกันได้ในปีที่ผลผลิตตกต่ำ
พฤติกรรมหลีกเลี่ยงความเสี่ยงนี้จำกัดการเติบโตและนวัตกรรมในระบบเศรษฐกิจ เนื่องจากโอกาสในการอยู่รอดมีค่าสูงกว่าความหวังต่อความมั่งคั่ง และนำไปสู่การครอบงำของวัฒนธรรมที่กดทับพฤติกรรมแปลกแยก วัฒนธรรมจึงเป็นกลไกปรับตัวที่เหมาะสมกับความแร้นแค้น ไม่ใช่เครื่องมือในการเปิดโอกาส
ในพื้นที่ที่เกษตรกรรมมีผลิตภาพสูง เช่น กรีซโบราณ กรรมสิทธิ์ส่วนตัว การออม และการเลื่อนสถานะทางสังคมก็เริ่มปรากฏ แต่ในพื้นที่ส่วนใหญ่ของโลก ระบบศักดินาครอบงำ เพราะผลิตภาพต่ำและมีความจำเป็นต้องพึ่งพาอำนาจผูกขาดความรุนแรง
บทนี้ยังวิเคราะห์การเปลี่ยนผ่านจากยุคโรมันไปสู่ยุคกลาง โดยเฉพาะ การปฏิวัติศักดินา ราวปี ค.ศ. 1000 การล่มสลายของจักรวรรดิโรมันทำให้รัฐอ่อนแอ และเปิดโอกาสให้ชาวนารายย่อยมีอิสระมากขึ้นในยุคมืด แต่เมื่อประชากรเพิ่มขึ้น ภูมิอากาศแปรปรวน และภัยพิบัติเกิดขึ้นต่อเนื่อง ผลผลิตตกต่ำ ชาวนาไม่สามารถรักษากรรมสิทธิ์ของตนไว้ได้ ต้องมอบที่ดินให้กับผู้มีอำนาจเพื่อแลกกับความคุ้มครอง กระบวนการนี้ค่อย ๆ เปลี่ยนเจ้าของที่ดินรายย่อยให้กลายเป็นไพร่ในระบบศักดินา
กองกำลังติดอาวุธ เช่น อัศวินม้า มีบทบาทสำคัญในการรวมอำนาจ เพราะมีต้นทุนการจัดหาสูงจนชาวนาทั่วไปไม่สามารถแข่งขันได้ โบสถ์จึงเข้ามามีบทบาทในการจำกัดความรุนแรงผ่านขบวนการ สันติภาพของพระเจ้า และยังมีบทบาทในเชิงโครงสร้างอื่น ๆ เช่น การศึกษา การจัดเก็บความรู้ การพัฒนาเกษตรกรรม และการก่อสร้างโครงสร้างพื้นฐาน เช่น ถนน เขื่อน และโรงสี
ตรรกะของความรุนแรงเปลี่ยนไปอย่างสิ้นเชิงในยุคเกษตรกรรม เพราะทรัพย์สินสามารถแย่งชิงได้ มีต้นทุนในการปกป้อง และผลตอบแทนที่คุ้มต่อการลงทุนในอาวุธ ความรุนแรงจึงกลายเป็นสิ่งที่ “คุ้มค่า” ทางเศรษฐศาสตร์เป็นครั้งแรกในประวัติศาสตร์
บทสรุปของบทนี้ชี้ให้เห็นว่า การเปลี่ยนแปลงจากยุคนักล่าสัตว์มาสู่การเกษตรคือจุดเริ่มต้นของระบบอำนาจ และเสรีภาพส่วนบุคคลถูกลดทอนลงเรื่อย ๆ เพื่อตอบสนองต่อความมั่นคงของทรัพย์สิน ในแง่นี้ เรื่องราวของคาอินผู้สังหารน้องชาย ซึ่งเป็นคนเลี้ยงสัตว์ สะท้อนถึงการก้าวเข้าสู่ยุคใหม่ที่การเพาะปลูกไม่เพียงสร้างอารยธรรม แต่ยังเปิดประตูสู่ตรรกะของการใช้ความรุนแรงอย่างเป็นระบบ
สามารถไปติดตามเนื้อหาแบบ short vdo ที่สรุปประเด็นสำคัญจากแต่ละบท พร้อมกราฟิกและคำอธิบายกระชับ เข้าใจง่าย ได้ที่ TikTok ช่อง https://www.tiktok.com/@moneyment1971
-
 @ c631e267:c2b78d3e
2025-04-20 19:54:32
@ c631e267:c2b78d3e
2025-04-20 19:54:32Es ist völlig unbestritten, dass der Angriff der russischen Armee auf die Ukraine im Februar 2022 strikt zu verurteilen ist. Ebenso unbestritten ist Russland unter Wladimir Putin keine brillante Demokratie. Aus diesen Tatsachen lässt sich jedoch nicht das finstere Bild des russischen Präsidenten – und erst recht nicht des Landes – begründen, das uns durchweg vorgesetzt wird und den Kern des aktuellen europäischen Bedrohungs-Szenarios darstellt. Da müssen wir schon etwas genauer hinschauen.
Der vorliegende Artikel versucht derweil nicht, den Einsatz von Gewalt oder die Verletzung von Menschenrechten zu rechtfertigen oder zu entschuldigen – ganz im Gegenteil. Dass jedoch der Verdacht des «Putinverstehers» sofort latent im Raume steht, verdeutlicht, was beim Thema «Russland» passiert: Meinungsmache und Manipulation.
Angesichts der mentalen Mobilmachung seitens Politik und Medien sowie des Bestrebens, einen bevorstehenden Krieg mit Russland geradezu herbeizureden, ist es notwendig, dieser fatalen Entwicklung entgegenzutreten. Wenn wir uns nur ein wenig von der herrschenden Schwarz-Weiß-Malerei freimachen, tauchen automatisch Fragen auf, die Risse im offiziellen Narrativ enthüllen. Grund genug, nachzuhaken.
Wer sich schon länger auch abseits der Staats- und sogenannten Leitmedien informiert, der wird in diesem Artikel vermutlich nicht viel Neues erfahren. Andere könnten hier ein paar unbekannte oder vergessene Aspekte entdecken. Möglicherweise klärt sich in diesem Kontext die Wahrnehmung der aktuellen (unserer eigenen!) Situation ein wenig.
Manipulation erkennen
Corona-«Pandemie», menschengemachter Klimawandel oder auch Ukraine-Krieg: Jede Menge Krisen, und für alle gibt es ein offizielles Narrativ, dessen Hinterfragung unerwünscht ist. Nun ist aber ein Narrativ einfach eine Erzählung, eine Geschichte (Latein: «narratio») und kein Tatsachenbericht. Und so wie ein Märchen soll auch das Narrativ eine Botschaft vermitteln.
Über die Methoden der Manipulation ist viel geschrieben worden, sowohl in Bezug auf das Individuum als auch auf die Massen. Sehr wertvolle Tipps dazu, wie man Manipulationen durchschauen kann, gibt ein Büchlein [1] von Albrecht Müller, dem Herausgeber der NachDenkSeiten.
Die Sprache selber eignet sich perfekt für die Manipulation. Beispielsweise kann die Wortwahl Bewertungen mitschwingen lassen, regelmäßiges Wiederholen (gerne auch von verschiedenen Seiten) lässt Dinge irgendwann «wahr» erscheinen, Übertreibungen fallen auf und hinterlassen wenigstens eine Spur im Gedächtnis, genauso wie Andeutungen. Belege spielen dabei keine Rolle.
Es gibt auffällig viele Sprachregelungen, die offenbar irgendwo getroffen und irgendwie koordiniert werden. Oder alle Redenschreiber und alle Medien kopieren sich neuerdings permanent gegenseitig. Welchen Zweck hat es wohl, wenn der Krieg in der Ukraine durchgängig und quasi wörtlich als «russischer Angriffskrieg auf die Ukraine» bezeichnet wird? Obwohl das in der Sache richtig ist, deutet die Art der Verwendung auf gezielte Beeinflussung hin und soll vor allem das Feindbild zementieren.
Sprachregelungen dienen oft der Absicherung einer einseitigen Darstellung. Das Gleiche gilt für das Verkürzen von Informationen bis hin zum hartnäckigen Verschweigen ganzer Themenbereiche. Auch hierfür gibt es rund um den Ukraine-Konflikt viele gute Beispiele.
Das gewünschte Ergebnis solcher Methoden ist eine Schwarz-Weiß-Malerei, bei der einer eindeutig als «der Böse» markiert ist und die anderen automatisch «die Guten» sind. Das ist praktisch und demonstriert gleichzeitig ein weiteres Manipulationswerkzeug: die Verwendung von Doppelstandards. Wenn man es schafft, bei wichtigen Themen regelmäßig mit zweierlei Maß zu messen, ohne dass das Publikum protestiert, dann hat man freie Bahn.
Experten zu bemühen, um bestimmte Sachverhalte zu erläutern, ist sicher sinnvoll, kann aber ebenso missbraucht werden, schon allein durch die Auswahl der jeweiligen Spezialisten. Seit «Corona» werden viele erfahrene und ehemals hoch angesehene Fachleute wegen der «falschen Meinung» diffamiert und gecancelt. [2] Das ist nicht nur ein brutaler Umgang mit Menschen, sondern auch eine extreme Form, die öffentliche Meinung zu steuern.
Wann immer wir also erkennen (weil wir aufmerksam waren), dass wir bei einem bestimmten Thema manipuliert werden, dann sind zwei logische und notwendige Fragen: Warum? Und was ist denn richtig? In unserem Russland-Kontext haben die Antworten darauf viel mit Geopolitik und Geschichte zu tun.
Ist Russland aggressiv und expansiv?
Angeblich plant Russland, europäische NATO-Staaten anzugreifen, nach dem Motto: «Zuerst die Ukraine, dann den Rest». In Deutschland weiß man dafür sogar das Datum: «Wir müssen bis 2029 kriegstüchtig sein», versichert Verteidigungsminister Pistorius.
Historisch gesehen ist es allerdings eher umgekehrt: Russland, bzw. die Sowjetunion, ist bereits dreimal von Westeuropa aus militärisch angegriffen worden. Die Feldzüge Napoleons, des deutschen Kaiserreichs und Nazi-Deutschlands haben Millionen Menschen das Leben gekostet. Bei dem ausdrücklichen Vernichtungskrieg ab 1941 kam es außerdem zu Brutalitäten wie der zweieinhalbjährigen Belagerung Leningrads (heute St. Petersburg) durch Hitlers Wehrmacht. Deren Ziel, die Bevölkerung auszuhungern, wurde erreicht: über eine Million tote Zivilisten.
Trotz dieser Erfahrungen stimmte Michail Gorbatschow 1990 der deutschen Wiedervereinigung zu und die Sowjetunion zog ihre Truppen aus Osteuropa zurück (vgl. Abb. 1). Der Warschauer Pakt wurde aufgelöst, der Kalte Krieg formell beendet. Die Sowjets erhielten damals von führenden westlichen Politikern die Zusicherung, dass sich die NATO «keinen Zentimeter ostwärts» ausdehnen würde, das ist dokumentiert. [3]

Expandiert ist die NATO trotzdem, und zwar bis an Russlands Grenzen (vgl. Abb. 2). Laut dem Politikberater Jeffrey Sachs handelt es sich dabei um ein langfristiges US-Projekt, das von Anfang an die Ukraine und Georgien mit einschloss. Offiziell wurde der Beitritt beiden Staaten 2008 angeboten. In jedem Fall könnte die massive Ost-Erweiterung seit 1999 aus russischer Sicht nicht nur als Vertrauensbruch, sondern durchaus auch als aggressiv betrachtet werden.

Russland hat den europäischen Staaten mehrfach die Hand ausgestreckt [4] für ein friedliches Zusammenleben und den «Aufbau des europäischen Hauses». Präsident Putin sei «in seiner ersten Amtszeit eine Chance für Europa» gewesen, urteilt die Journalistin und langjährige Russland-Korrespondentin der ARD, Gabriele Krone-Schmalz. Er habe damals viele positive Signale Richtung Westen gesendet.
Die Europäer jedoch waren scheinbar an einer Partnerschaft mit dem kontinentalen Nachbarn weniger interessiert als an der mit dem transatlantischen Hegemon. Sie verkennen bis heute, dass eine gedeihliche Zusammenarbeit in Eurasien eine Gefahr für die USA und deren bekundetes Bestreben ist, die «einzige Weltmacht» zu sein – «Full Spectrum Dominance» [5] nannte das Pentagon das. Statt einem neuen Kalten Krieg entgegenzuarbeiten, ließen sich europäische Staaten selber in völkerrechtswidrige «US-dominierte Angriffskriege» [6] verwickeln, wie in Serbien, Afghanistan, dem Irak, Libyen oder Syrien. Diese werden aber selten so benannt.

Speziell den Deutschen stünde außer einer Portion Realismus auch etwas mehr Dankbarkeit gut zu Gesicht. Das Geschichtsbewusstsein der Mehrheit scheint doch recht selektiv und das Selbstbewusstsein einiger etwas desorientiert zu sein. Bekanntermaßen waren es die Soldaten der sowjetischen Roten Armee, die unter hohen Opfern 1945 Deutschland «vom Faschismus befreit» haben. Bei den Gedenkfeiern zu 80 Jahren Kriegsende will jedoch das Auswärtige Amt – noch unter der Diplomatie-Expertin Baerbock, die sich schon länger offiziell im Krieg mit Russland wähnt, – nun keine Russen sehen: Sie sollen notfalls rausgeschmissen werden.
«Die Grundsatzfrage lautet: Geht es Russland um einen angemessenen Platz in einer globalen Sicherheitsarchitektur, oder ist Moskau schon seit langem auf einem imperialistischen Trip, der befürchten lassen muss, dass die Russen in fünf Jahren in Berlin stehen?»
So bringt Gabriele Krone-Schmalz [7] die eigentliche Frage auf den Punkt, die zur Einschätzung der Situation letztlich auch jeder für sich beantworten muss.
Was ist los in der Ukraine?
In der internationalen Politik geht es nie um Demokratie oder Menschenrechte, sondern immer um Interessen von Staaten. Diese These stammt von Egon Bahr, einem der Architekten der deutschen Ostpolitik des «Wandels durch Annäherung» aus den 1960er und 70er Jahren. Sie trifft auch auf den Ukraine-Konflikt zu, den handfeste geostrategische und wirtschaftliche Interessen beherrschen, obwohl dort angeblich «unsere Demokratie» verteidigt wird.
Es ist ein wesentliches Element des Ukraine-Narrativs und Teil der Manipulation, die Vorgeschichte des Krieges wegzulassen – mindestens die vor der russischen «Annexion» der Halbinsel Krim im März 2014, aber oft sogar komplett diejenige vor der Invasion Ende Februar 2022. Das Thema ist komplex, aber einige Aspekte, die für eine Beurteilung nicht unwichtig sind, will ich wenigstens kurz skizzieren. [8]
Das Gebiet der heutigen Ukraine und Russlands – die übrigens in der «Kiewer Rus» gemeinsame Wurzeln haben – hat der britische Geostratege Halford Mackinder bereits 1904 als eurasisches «Heartland» bezeichnet, dessen Kontrolle er eine große Bedeutung für die imperiale Strategie Großbritanniens zumaß. Für den ehemaligen Sicherheits- und außenpolitischen Berater mehrerer US-amerikanischer Präsidenten und Mitgründer der Trilateralen Kommission, Zbigniew Brzezinski, war die Ukraine nach der Auflösung der Sowjetunion ein wichtiger Spielstein auf dem «eurasischen Schachbrett», wegen seiner Nähe zu Russland, seiner Bodenschätze und seines Zugangs zum Schwarzen Meer.
Die Ukraine ist seit langem ein gespaltenes Land. Historisch zerrissen als Spielball externer Interessen und geprägt von ethnischen, kulturellen, religiösen und geografischen Unterschieden existiert bis heute, grob gesagt, eine Ost-West-Spaltung, welche die Suche nach einer nationalen Identität stark erschwert.
Insbesondere im Zuge der beiden Weltkriege sowie der Russischen Revolution entstanden tiefe Risse in der Bevölkerung. Ukrainer kämpften gegen Ukrainer, zum Beispiel die einen auf der Seite von Hitlers faschistischer Nazi-Armee und die anderen auf der von Stalins kommunistischer Roter Armee. Die Verbrechen auf beiden Seiten sind nicht vergessen. Dass nach der Unabhängigkeit 1991 versucht wurde, Figuren wie den radikalen Nationalisten Symon Petljura oder den Faschisten und Nazi-Kollaborateur Stepan Bandera als «Nationalhelden» zu installieren, verbessert die Sache nicht.
Während die USA und EU-Staaten zunehmend «ausländische Einmischung» (speziell russische) in «ihre Demokratien» wittern, betreiben sie genau dies seit Jahrzehnten in vielen Ländern der Welt. Die seit den 2000er Jahren bekannten «Farbrevolutionen» in Osteuropa werden oft als Methode des Regierungsumsturzes durch von außen gesteuerte «demokratische» Volksaufstände beschrieben. Diese Strategie geht auf Analysen zum «Schwarmverhalten» [9] seit den 1960er Jahren zurück (Studentenproteste), wo es um die potenzielle Wirksamkeit einer «rebellischen Hysterie» von Jugendlichen bei postmodernen Staatsstreichen geht. Heute nennt sich dieses gezielte Kanalisieren der Massen zur Beseitigung unkooperativer Regierungen «Soft-Power».
In der Ukraine gab es mit der «Orangen Revolution» 2004 und dem «Euromaidan» 2014 gleich zwei solcher «Aufstände». Der erste erzwang wegen angeblicher Unregelmäßigkeiten eine Wiederholung der Wahlen, was mit Wiktor Juschtschenko als neuem Präsidenten endete. Dieser war ehemaliger Direktor der Nationalbank und Befürworter einer Annäherung an EU und NATO. Seine Frau, die First Lady, ist US-amerikanische «Philanthropin» und war Beamtin im Weißen Haus in der Reagan- und der Bush-Administration.
Im Gegensatz zu diesem ersten Event endete der sogenannte Euromaidan unfriedlich und blutig. Die mehrwöchigen Proteste gegen Präsident Wiktor Janukowitsch, in Teilen wegen des nicht unterzeichneten Assoziierungsabkommens mit der EU, wurden zunehmend gewalttätiger und von Nationalisten und Faschisten des «Rechten Sektors» dominiert. Sie mündeten Ende Februar 2014 auf dem Kiewer Unabhängigkeitsplatz (Maidan) in einem Massaker durch Scharfschützen. Dass deren Herkunft und die genauen Umstände nicht geklärt wurden, störte die Medien nur wenig. [10]
Janukowitsch musste fliehen, er trat nicht zurück. Vielmehr handelte es sich um einen gewaltsamen, allem Anschein nach vom Westen inszenierten Putsch. Laut Jeffrey Sachs war das kein Geheimnis, außer vielleicht für die Bürger. Die USA unterstützten die Post-Maidan-Regierung nicht nur, sie beeinflussten auch ihre Bildung. Das geht unter anderem aus dem berühmten «Fuck the EU»-Telefonat der US-Chefdiplomatin für die Ukraine, Victoria Nuland, mit Botschafter Geoffrey Pyatt hervor.
Dieser Bruch der demokratischen Verfassung war letztlich der Auslöser für die anschließenden Krisen auf der Krim und im Donbass (Ostukraine). Angesichts der ukrainischen Geschichte mussten die nationalistischen Tendenzen und die Beteiligung der rechten Gruppen an dem Umsturz bei der russigsprachigen Bevölkerung im Osten ungute Gefühle auslösen. Es gab Kritik an der Übergangsregierung, Befürworter einer Abspaltung und auch für einen Anschluss an Russland.
Ebenso konnte Wladimir Putin in dieser Situation durchaus Bedenken wegen des Status der russischen Militärbasis für seine Schwarzmeerflotte in Sewastopol auf der Krim haben, für die es einen langfristigen Pachtvertrag mit der Ukraine gab. Was im März 2014 auf der Krim stattfand, sei keine Annexion, sondern eine Abspaltung (Sezession) nach einem Referendum gewesen, also keine gewaltsame Aneignung, urteilte der Rechtswissenschaftler Reinhard Merkel in der FAZ sehr detailliert begründet. Übrigens hatte die Krim bereits zu Zeiten der Sowjetunion den Status einer autonomen Republik innerhalb der Ukrainischen SSR.
Anfang April 2014 wurden in der Ostukraine die «Volksrepubliken» Donezk und Lugansk ausgerufen. Die Kiewer Übergangsregierung ging unter der Bezeichnung «Anti-Terror-Operation» (ATO) militärisch gegen diesen, auch von Russland instrumentalisierten Widerstand vor. Zufällig war kurz zuvor CIA-Chef John Brennan in Kiew. Die Maßnahmen gingen unter dem seit Mai neuen ukrainischen Präsidenten, dem Milliardär Petro Poroschenko, weiter. Auch Wolodymyr Selenskyj beendete den Bürgerkrieg nicht, als er 2019 vom Präsidenten-Schauspieler, der Oligarchen entmachtet, zum Präsidenten wurde. Er fuhr fort, die eigene Bevölkerung zu bombardieren.
Mit dem Einmarsch russischer Truppen in die Ostukraine am 24. Februar 2022 begann die zweite Phase des Krieges. Die Wochen und Monate davor waren intensiv. Im November hatte die Ukraine mit den USA ein Abkommen über eine «strategische Partnerschaft» unterzeichnet. Darin sagten die Amerikaner ihre Unterstützung der EU- und NATO-Perspektive der Ukraine sowie quasi für die Rückeroberung der Krim zu. Dagegen ließ Putin der NATO und den USA im Dezember 2021 einen Vertragsentwurf über beiderseitige verbindliche Sicherheitsgarantien zukommen, den die NATO im Januar ablehnte. Im Februar eskalierte laut OSZE die Gewalt im Donbass.
Bereits wenige Wochen nach der Invasion, Ende März 2022, kam es in Istanbul zu Friedensverhandlungen, die fast zu einer Lösung geführt hätten. Dass der Krieg nicht damals bereits beendet wurde, lag daran, dass der Westen dies nicht wollte. Man war der Meinung, Russland durch die Ukraine in diesem Stellvertreterkrieg auf Dauer militärisch schwächen zu können. Angesichts von Hunderttausenden Toten, Verletzten und Traumatisierten, die als Folge seitdem zu beklagen sind, sowie dem Ausmaß der Zerstörung, fehlen einem die Worte.
Hasst der Westen die Russen?
Diese Frage drängt sich auf, wenn man das oft unerträglich feindselige Gebaren beobachtet, das beileibe nicht neu ist und vor Doppelmoral trieft. Russland und speziell die Person Wladimir Putins werden regelrecht dämonisiert, was gleichzeitig scheinbar jede Form von Diplomatie ausschließt.
Russlands militärische Stärke, seine geografische Lage, sein Rohstoffreichtum oder seine unabhängige diplomatische Tradition sind sicher Störfaktoren für das US-amerikanische Bestreben, der Boss in einer unipolaren Welt zu sein. Ein womöglich funktionierender eurasischer Kontinent, insbesondere gute Beziehungen zwischen Russland und Deutschland, war indes schon vor dem Ersten Weltkrieg eine Sorge des britischen Imperiums.
Ein «Vergehen» von Präsident Putin könnte gewesen sein, dass er die neoliberale Schocktherapie à la IWF und den Ausverkauf des Landes (auch an US-Konzerne) beendete, der unter seinem Vorgänger herrschte. Dabei zeigte er sich als Führungspersönlichkeit und als nicht so formbar wie Jelzin. Diese Aspekte allein sind aber heute vermutlich keine ausreichende Erklärung für ein derart gepflegtes Feindbild.
Der Historiker und Philosoph Hauke Ritz erweitert den Fokus der Fragestellung zu: «Warum hasst der Westen die Russen so sehr?», was er zum Beispiel mit dem Medienforscher Michael Meyen und mit der Politikwissenschaftlerin Ulrike Guérot bespricht. Ritz stellt die interessante These [11] auf, dass Russland eine Provokation für den Westen sei, welcher vor allem dessen kulturelles und intellektuelles Potenzial fürchte.
Die Russen sind Europäer aber anders, sagt Ritz. Diese «Fremdheit in der Ähnlichkeit» erzeuge vielleicht tiefe Ablehnungsgefühle. Obwohl Russlands Identität in der europäischen Kultur verwurzelt ist, verbinde es sich immer mit der Opposition in Europa. Als Beispiele nennt er die Kritik an der katholischen Kirche oder die Verbindung mit der Arbeiterbewegung. Christen, aber orthodox; Sozialismus statt Liberalismus. Das mache das Land zum Antagonisten des Westens und zu einer Bedrohung der Machtstrukturen in Europa.
Fazit
Selbstverständlich kann man Geschichte, Ereignisse und Entwicklungen immer auf verschiedene Arten lesen. Dieser Artikel, obwohl viel zu lang, konnte nur einige Aspekte der Ukraine-Tragödie anreißen, die in den offiziellen Darstellungen in der Regel nicht vorkommen. Mindestens dürfte damit jedoch klar geworden sein, dass die Russische Föderation bzw. Wladimir Putin nicht der alleinige Aggressor in diesem Konflikt ist. Das ist ein Stellvertreterkrieg zwischen USA/NATO (gut) und Russland (böse); die Ukraine (edel) wird dabei schlicht verheizt.
Das ist insofern von Bedeutung, als die gesamte europäische Kriegshysterie auf sorgsam kultivierten Freund-Feind-Bildern beruht. Nur so kann Konfrontation und Eskalation betrieben werden, denn damit werden die wahren Hintergründe und Motive verschleiert. Angst und Propaganda sind notwendig, damit die Menschen den Wahnsinn mitmachen. Sie werden belogen, um sie zuerst zu schröpfen und anschließend auf die Schlachtbank zu schicken. Das kann niemand wollen, außer den stets gleichen Profiteuren: die Rüstungs-Lobby und die großen Investoren, die schon immer an Zerstörung und Wiederaufbau verdient haben.
Apropos Investoren: Zu den Top-Verdienern und somit Hauptinteressenten an einer Fortführung des Krieges zählt BlackRock, einer der weltgrößten Vermögensverwalter. Der deutsche Bundeskanzler in spe, Friedrich Merz, der gerne «Taurus»-Marschflugkörper an die Ukraine liefern und die Krim-Brücke zerstören möchte, war von 2016 bis 2020 Aufsichtsratsvorsitzender von BlackRock in Deutschland. Aber das hat natürlich nichts zu sagen, der Mann macht nur seinen Job.
Es ist ein Spiel der Kräfte, es geht um Macht und strategische Kontrolle, um Geheimdienste und die Kontrolle der öffentlichen Meinung, um Bodenschätze, Rohstoffe, Pipelines und Märkte. Das klingt aber nicht sexy, «Demokratie und Menschenrechte» hört sich besser und einfacher an. Dabei wäre eine für alle Seiten förderliche Politik auch nicht so kompliziert; das Handwerkszeug dazu nennt sich Diplomatie. Noch einmal Gabriele Krone-Schmalz:
«Friedliche Politik ist nichts anderes als funktionierender Interessenausgleich. Da geht’s nicht um Moral.»
Die Situation in der Ukraine ist sicher komplex, vor allem wegen der inneren Zerrissenheit. Es dürfte nicht leicht sein, eine friedliche Lösung für das Zusammenleben zu finden, aber die Beteiligten müssen es vor allem wollen. Unter den gegebenen Umständen könnte eine sinnvolle Perspektive mit Neutralität und föderalen Strukturen zu tun haben.
Allen, die sich bis hierher durch die Lektüre gearbeitet (oder auch einfach nur runtergescrollt) haben, wünsche ich frohe Oster-Friedenstage!
[Titelbild: Pixabay; Abb. 1 und 2: nach Ganser/SIPER; Abb. 3: SIPER]
--- Quellen: ---
[1] Albrecht Müller, «Glaube wenig. Hinterfrage alles. Denke selbst.», Westend 2019
[2] Zwei nette Beispiele:
- ARD-faktenfinder (sic), «Viel Aufmerksamkeit für fragwürdige Experten», 03/2023
- Neue Zürcher Zeitung, «Aufstieg und Fall einer Russlandversteherin – die ehemalige ARD-Korrespondentin Gabriele Krone-Schmalz rechtfertigt seit Jahren Putins Politik», 12/2022
[3] George Washington University, «NATO Expansion: What Gorbachev Heard – Declassified documents show security assurances against NATO expansion to Soviet leaders from Baker, Bush, Genscher, Kohl, Gates, Mitterrand, Thatcher, Hurd, Major, and Woerner», 12/2017
[4] Beispielsweise Wladimir Putin bei seiner Rede im Deutschen Bundestag, 25/09/2001
[5] William Engdahl, «Full Spectrum Dominance, Totalitarian Democracy In The New World Order», edition.engdahl 2009
[6] Daniele Ganser, «Illegale Kriege – Wie die NATO-Länder die UNO sabotieren. Eine Chronik von Kuba bis Syrien», Orell Füssli 2016
[7] Gabriele Krone-Schmalz, «Mit Friedensjournalismus gegen ‘Kriegstüchtigkeit’», Vortrag und Diskussion an der Universität Hamburg, veranstaltet von engagierten Studenten, 16/01/2025\ → Hier ist ein ähnlicher Vortrag von ihr (Video), den ich mit spanischer Übersetzung gefunden habe.
[8] Für mehr Hintergrund und Details empfehlen sich z.B. folgende Bücher:
- Mathias Bröckers, Paul Schreyer, «Wir sind immer die Guten», Westend 2019
- Gabriele Krone-Schmalz, «Russland verstehen? Der Kampf um die Ukraine und die Arroganz des Westens», Westend 2023
- Patrik Baab, «Auf beiden Seiten der Front – Meine Reisen in die Ukraine», Fiftyfifty 2023
[9] vgl. Jonathan Mowat, «Washington's New World Order "Democratization" Template», 02/2005 und RAND Corporation, «Swarming and the Future of Conflict», 2000
[10] Bemerkenswert einige Beiträge, von denen man später nichts mehr wissen wollte:
- ARD Monitor, «Todesschüsse in Kiew: Wer ist für das Blutbad vom Maidan verantwortlich», 10/04/2014, Transkript hier
- Telepolis, «Blutbad am Maidan: Wer waren die Todesschützen?», 12/04/2014
- Telepolis, «Scharfschützenmorde in Kiew», 14/12/2014
- Deutschlandfunk, «Gefahr einer Spirale nach unten», Interview mit Günter Verheugen, 18/03/2014
- NDR Panorama, «Putsch in Kiew: Welche Rolle spielen die Faschisten?», 06/03/2014
[11] Hauke Ritz, «Vom Niedergang des Westens zur Neuerfindung Europas», 2024
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ c631e267:c2b78d3e
2025-04-18 15:53:07
@ c631e267:c2b78d3e
2025-04-18 15:53:07Verstand ohne Gefühl ist unmenschlich; \ Gefühl ohne Verstand ist Dummheit. \ Egon Bahr
Seit Jahren werden wir darauf getrimmt, dass Fakten eigentlich gefühlt seien. Aber nicht alles ist relativ und nicht alles ist nach Belieben interpretierbar. Diese Schokoladenhasen beispielsweise, die an Ostern in unseren Gefilden typisch sind, «ostern» zwar nicht, sondern sie sitzen in der Regel, trotzdem verwandelt sie das nicht in «Sitzhasen».
Nichts soll mehr gelten, außer den immer invasiveren Gesetzen. Die eigenen Traditionen und Wurzeln sind potenziell «pfui», um andere Menschen nicht auszuschließen, aber wir mögen uns toleranterweise an die fremden Symbole und Rituale gewöhnen. Dabei ist es mir prinzipiell völlig egal, ob und wann jemand ein Fastenbrechen feiert, am Karsamstag oder jedem anderen Tag oder nie – aber bitte freiwillig.
Und vor allem: Lasst die Finger von den Kindern! In Bern setzten kürzlich Demonstranten ein Zeichen gegen die zunehmende Verbreitung woker Ideologie im Bildungssystem und forderten ein Ende der sexuellen Indoktrination von Schulkindern.
Wenn es nicht wegen des heiklen Themas Migration oder wegen des Regenbogens ist, dann wegen des Klimas. Im Rahmen der «Netto Null»-Agenda zum Kampf gegen das angeblich teuflische CO2 sollen die Menschen ihre Ernährungsgewohnheiten komplett ändern. Nach dem Willen von Produzenten synthetischer Lebensmittel, wie Bill Gates, sollen wir baldmöglichst praktisch auf Fleisch und alle Milchprodukte wie Milch und Käse verzichten. Ein lukratives Geschäftsmodell, das neben der EU aktuell auch von einem britischen Lobby-Konsortium unterstützt wird.
Sollten alle ideologischen Stricke zu reißen drohen, ist da immer noch «der Putin». Die Unions-Europäer offenbaren sich dabei ständig mehr als Vertreter der Rüstungsindustrie. Allen voran zündelt Deutschland an der Kriegslunte, angeführt von einem scheinbar todesmutigen Kanzlerkandidaten Friedrich Merz. Nach dessen erneuter Aussage, «Taurus»-Marschflugkörper an Kiew liefern zu wollen, hat Russland eindeutig klargestellt, dass man dies als direkte Kriegsbeteiligung werten würde – «mit allen sich daraus ergebenden Konsequenzen für Deutschland».
Wohltuend sind Nachrichten über Aktivitäten, die sich der allgemeinen Kriegstreiberei entgegenstellen oder diese öffentlich hinterfragen. Dazu zählt auch ein Kongress kritischer Psychologen und Psychotherapeuten, der letzte Woche in Berlin stattfand. Die vielen Vorträge im Kontext von «Krieg und Frieden» deckten ein breites Themenspektrum ab, darunter Friedensarbeit oder die Notwendigkeit einer «Pädagogik der Kriegsuntüchtigkeit».
Der heutige «stille Freitag», an dem Christen des Leidens und Sterbens von Jesus gedenken, ist vielleicht unabhängig von jeder religiösen oder spirituellen Prägung eine passende Einladung zur Reflexion. In der Ruhe liegt die Kraft. In diesem Sinne wünsche ich Ihnen frohe Ostertage!
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ a3c6f928:d45494fb
2025-05-10 09:36:24
@ a3c6f928:d45494fb
2025-05-10 09:36:24In today's hyper-connected world, the concept of freedom has taken on new dimensions. With every click, swipe, and search, we contribute to a vast digital footprint that shapes how we are seen and how we interact with the world. But as technology advances, so too does the tension between digital convenience and the right to personal privacy.
The Digital Landscape
The rise of the internet has democratized information, connecting billions of people across the globe. Social media platforms allow for unprecedented levels of communication, giving a voice to the voiceless and a platform for activism. However, this connectivity comes with a price—our personal information.
The Cost of Convenience
From targeted ads to personalized recommendations, our online behaviors are tracked, analyzed, and sometimes exploited. While this can enhance user experience, it also raises questions about how much of our freedom is being surrendered in exchange for convenience. Are we willingly giving up our privacy for the sake of digital ease?
Privacy vs. Security
Governments and corporations argue that data collection is necessary for security and better services. However, this often blurs the lines between protection and intrusion. When is it acceptable for private information to be shared, and where should the boundaries be drawn?
Protecting Digital Freedom
-
Know Your Rights: Understand the privacy policies of the platforms you use.
-
Use Encryption: Protect your personal communications with encrypted services.
-
Limit Data Sharing: Be mindful of the information you share online.
-
Support Digital Rights: Advocate for stronger data protection laws.
The Path Forward
As technology continues to evolve, so must our understanding of freedom in the digital realm. True digital freedom is not just about access; it is about control—control over our information, our choices, and our online identities.
“The price of freedom is eternal vigilance.” — Thomas Jefferson
In this digital age, that vigilance must extend to the virtual world, where our freedoms are just as valuable and just as fragile.
-
-
 @ 3eba5ef4:751f23ae
2025-05-09 01:49:00
@ 3eba5ef4:751f23ae
2025-05-09 01:49:00加密洞见
取消 OP_RETURN 限制?引发比特币开发者激辩论
OP_RETURN 于 2014 年推出,允许将小块数据(如时间戳或短消息)包含在比特币交易中,作为在比特币链上存储有限信息的轻量级方式。出于防止垃圾信息的考虑,OP_RETURN 当前的大小限制是 83 字节。
Peter Todd 最近提议完全取消该限制。他认为该限制无法有效遏制滥用,反倒让事情更加复杂。因为它迫使一些开发人员采用各种变通方式——如使用 scriptsig 或不可花费输出(比如这里介绍了在无法花费的 Taproot 输出上存储数据的方式)——来存储媒体、垃圾信息和其他任意数据,这会导致 UTXO 集膨胀。
Pieter Wuille 同样主张 取消 OP_RETURN 限制。他认为,标准性策略并不太可能真正阻止那些由资金充足的组织创建的数据交易被确认——这些组织会将交易直接发送给矿工。此外,现在网络中的区块基本始终满载——即便是没有垃圾信息——因此 OP_RETURN 限制这样的规则已经没有效用。
总之,支持取消 OP_Return 限制一方的理由是,该限制是徒劳的,区块内已经有其它数据存储的替代方案。
反对该提案的一方则认为必须保留该限制,因为通过 OP_Return 存储任意数据违反了中本聪的初衷,也偏离了比特币作为金融网络的核心目的(Luke Dashjr)。其他反对意见包括: - 来自 Ocean Mining 的 @Mechanic:「开发者凭直觉就知道,不应用比特币来存储任意文件,而且应该尽一切可能让比特币难以用于这个目的。」 - Jason Hughes:「Bitcoin Core 开发人员即将合并一项将比特币变成毫无价值的山寨币的更改」……
了解争论中的更多观点,可以参考这里。
三种集群线性化技术比较
Pieter Wuille 在本文中比较了 SFL (spanning-forest linearization)、GGT 、CSS (candidate set search) 三种集群线性化技术之间的基本权衡,并跟进了每种技术的实现基准。
StarkWare 推出 ColliderVM:用于计算和桥接的 BitVM 替代协议
ColliderVM 是 StarkWare 研究的一个 BitVM 的替代协议,使用与 BitVM 相同的信任假设,但不需要欺诈证明,同时也能实现更广泛的功能,如智能合约和二层桥接。
相关论文:ColliderVM: Stateful Computation on Bitcoin without Fraud Proofs
相关视频:Bitcoin Horizons: from OP_CAT to Covenants
剑桥研究:比特币挖矿正使用超过 50% 的绿色能源
剑桥替代金融中心(CCAF)的一份新报告称,现在 52.4% 的比特币挖矿由绿色能源提供动力,其中 42.6% 来自水力和风能等可再生能源,9.8% 来自核能。比特币矿工正在通过减少化石燃料的使用和更好地管理硬件废物来改善他们的环境足迹。
精彩无限,不止于链
如何识破朝鲜黑客?Kraken 分享招聘经验
Kraken 团队最近发现一名朝鲜黑客试图通过申请工作,于是就如何在招聘流程每个阶段中识别并防范黑客分享了经验。
带回绕的轮次高效自适应安全门限签名方案
门限签名方案允许将一个签名密钥分发给 n 个用户,使得其中任意 t 个用户可以联合生成签名,但任意 t−1 个用户则无法做到这一点。研究者希望门限签名方案(Threshold Signatures)能具备自适应安全性,即在面对能够在交互后动态腐化诚实用户的对手时仍然保持安全。对于一类依赖带回绕(rewinding)证明的签名方案(如 Schnorr 签名),证明其自适应安全性是一个重大挑战。论文提出了两种在带回绕证明下可证明具备自适应安全性的门限签名方案。其安全性证明完全基于随机预言机模型(ROM),不依赖代数群模型(AGM)。
论文全文:Round-Efficient Adaptively Secure Threshold Signatures with Rewinding
以太坊如何简化 L1,实现对标比特币的简洁架构
Vitalik 近日发表 Simplifying the L1 ,建议简化以太坊 L1,从 EVM 迁移到 RISC-V(或其他最小 VM),采用「简单序列化」(Simple Serialize),仿效 Tinygrad 的简洁代码风格。
特别地,关于 RISC-V,Vitalik 认为这一转变会带来:
- 效率革命性提升:在 ZK 证明者内部,智能合约可直接执行,无需解释器开销。Succinct 数据显示,在多数场景下性能可提升百倍以上。
- 结构极致简化:RISC-V 规范相较于EVM 极为精简,其他候选方案(如 Cairo)同样具备简洁特性。
- 继承 EOF 的所有优势:包括代码分段管理、更友好的静态分析支持,以及更大的代码容量限制。
- 开发者工具链扩展:Solidity 和 Vyper 可通过新增后端编译支持新架构;若选择 RISC-V,主流语言开发者可直接移植现有代码。
- 消除对大部分预编译的要求:也许除了保留高优化的椭圆曲线运算外,大部分预编译功能将不再必要(而椭圆曲线也许也会随量子计算发展被淘汰)。
-
 @ 502ab02a:a2860397
2025-05-09 01:07:20
@ 502ab02a:a2860397
2025-05-09 01:07:20ถ้าย้อนกลับไป 50 ปีก่อน ถ้าเฮียถามคำนี้กับลุงชาวนาคนหนึ่ง เขาคงหัวเราะแล้วตอบแบบไม่ต้องคิดว่า “ก็เจ้าของที่นาไงไอ้ทิด จะมีใครล่ะ?”
แต่พอมาในวันนี้ ถ้าเฮียถามคำเดิมในซูเปอร์มาร์เก็ต คงไม่มีใครกล้าตอบแบบนั้นอีกแล้ว เพราะแค่ในชั้นวางโยเกิร์ตเดียวกัน เฮียอาจเห็นยี่ห้อต่างกัน 10 ยี่ห้อ แต่ทั้งหมดอาจเป็นของบริษัทแม่เพียงเจ้าเดียว
ในศตวรรษที่ 21 อาหารไม่ใช่ของคนทำอาหาร แต่มันกลายเป็นของ บริษัทผู้ครอบครองข้อมูล พันธุกรรม และระบบการกระจายสินค้า โลกวันนี้ไม่ได้มีเกษตรกรล้อมวงเคี้ยวหมาก แต่มีบริษัทเทคโนโลยีจับมือกับนักลงทุนระดับโลก ถือครองเมล็ดพันธุ์ เป็นเจ้าของสิทธิบัตรจุลินทรีย์ในลำไส้ และมีอำนาจเสนอว่า “อาหารแบบไหนควรได้รับเงินสนับสนุนจากรัฐ”
บริษัทเทคโนโลยีในซิลิคอนแวลลีย์บางแห่ง ไม่ได้แค่ผลิตซอฟต์แวร์อีกต่อไป แต่เริ่มทำ "อาหารจากโค้ด" โปรตีนสังเคราะห์ที่ได้จากการแทรกยีน หรือแม้แต่ “อาหารจากคาร์บอนในอากาศ” ที่สร้างโดย AI เขาไม่ได้ปลูกข้าว แต่เขาเขียนสูตรให้เครื่องจักรสร้างอาหารในถัง
ใครมีสิทธิบัตร…คนนั้นคือเจ้าของ ใครควบคุมข้อมูลสุขภาพ…คนนั้นคือนายทุนแห่งความหิว และใครสามารถชี้นิ้วให้รัฐบาลเปลี่ยนนโยบายอาหารโรงเรียน…คนนั้นคือเจ้าของอนาคตของเด็กทั้งประเทศ
มันฟังดูเวอร์ใช่ไหม? แต่ลองดูดี ๆ…ใครเป็นเจ้าของฟาร์มหมู ฟาร์มไก่ โรงฆ่าสัตว์? หลายแห่งไม่ได้เป็นของชาวบ้านอีกต่อไป แต่เป็นของเครือบริษัทยักษ์ใหญ่ที่อยู่เบื้องหลังทั้งอาหารในซูเปอร์ และเม็ดวิตามินในกระปุกเฮียด้วย
ยิ่งไปกว่านั้น เจ้าของตัวจริงไม่ได้อยู่ในร้านของชำ แต่ซ่อนตัวอยู่ในบอร์ดบริหารบริษัทเกษตรข้ามชาติ ในเวทีประชุมเศรษฐกิจโลก และในห้องประชุมที่ตัดสินว่า “อาหารจากวัว” ควรถูกเก็บภาษีคาร์บอนเพิ่มหรือไม่
เมื่อก่อนเฮียเคยคิดว่า ถ้าเราปลูกผักเอง ก็คุมอาหารตัวเองได้ แต่พอระบบเริ่มขับไล่เมล็ดพันธุ์ดั้งเดิมให้สูญพันธุ์ ถ้าไม่มีใบอนุญาตปลูกพืช GMO หรือไม่มีเงินซื้อปุ๋ยจากบริษัทเดียวที่ยังอยู่รอด เกษตรกรจะเป็นเจ้าของอะไรกันแน่?
และคำว่า “อาหารอิสระ” ในยุคนี้ อาจไม่ใช่แค่การไม่พึ่งพาซูเปอร์ แต่มันคือ “การตื่นรู้ว่าใครเป็นคนจัดเกม และใครเป็นคนตั้งกฎ”
เพราะในยุคที่ทุกอย่างแปรรูปเป็นดิจิทัล แม้แต่อาหารก็อาจมีเจ้าของเพียงไม่กี่ราย และสิ่งที่น่ากลัวกว่าผูกขาด…คือการ “ผูกอนาคต” ของเราทั้งมื้อ
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ f32184ee:6d1c17bf
2025-04-23 13:21:52
@ f32184ee:6d1c17bf
2025-04-23 13:21:52Ads Fueling Freedom
Ross Ulbricht’s "Decentralize Social Media" painted a picture of a user-centric, decentralized future that transcended the limitations of platforms like the tech giants of today. Though focused on social media, his concept provided a blueprint for decentralized content systems writ large. The PROMO Protocol, designed by NextBlock while participating in Sovereign Engineering, embodies this blueprint in the realm of advertising, leveraging Nostr and Bitcoin’s Lightning Network to give individuals control, foster a multi-provider ecosystem, and ensure secure value exchange. In this way, Ulbricht’s 2021 vision can be seen as a prescient prediction of the PROMO Protocol’s structure. This is a testament to the enduring power of his ideas, now finding form in NextBlock’s innovative approach.
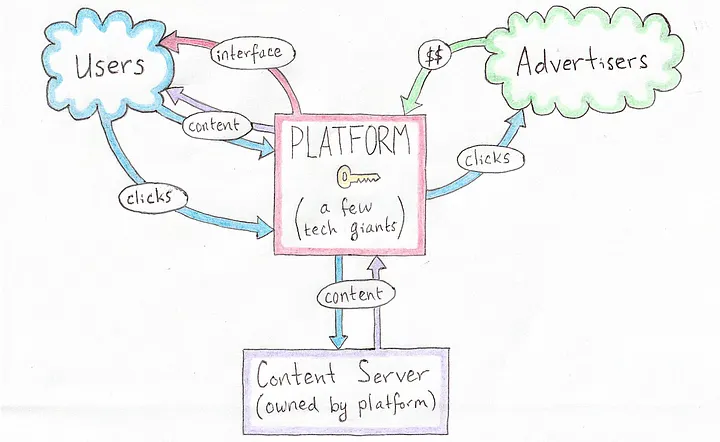 [Current Platform-Centric Paradigm, source: Ross Ulbricht's Decentralize Social Media]
[Current Platform-Centric Paradigm, source: Ross Ulbricht's Decentralize Social Media]Ulbricht’s Vision: A Decentralized Social Protocol
In his 2021 Medium article Ulbricht proposed a revolutionary vision for a decentralized social protocol (DSP) to address the inherent flaws of centralized social media platforms, such as privacy violations and inconsistent content moderation. Writing from prison, Ulbricht argued that decentralization could empower users by giving them control over their own content and the value they create, while replacing single, monolithic platforms with a competitive ecosystem of interface providers, content servers, and advertisers. Though his focus was on social media, Ulbricht’s ideas laid a conceptual foundation that strikingly predicts the structure of NextBlock’s PROMO Protocol, a decentralized advertising system built on the Nostr protocol.
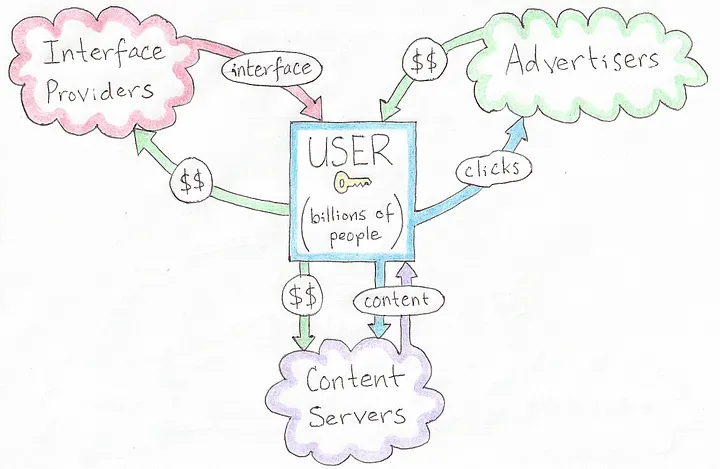 [A Decentralized Social Protocol (DSP), source: Ross Ulbricht's Decentralize Social Media]
[A Decentralized Social Protocol (DSP), source: Ross Ulbricht's Decentralize Social Media]Ulbricht’s Principles
Ulbricht’s article outlines several key principles for his DSP: * User Control: Users should own their content and dictate how their data and creations generate value, rather than being subject to the whims of centralized corporations. * Decentralized Infrastructure: Instead of a single platform, multiple interface providers, content hosts, and advertisers interoperate, fostering competition and resilience. * Privacy and Autonomy: Decentralized solutions for profile management, hosting, and interactions would protect user privacy and reduce reliance on unaccountable intermediaries. * Value Creation: Users, not platforms, should capture the economic benefits of their contributions, supported by decentralized mechanisms for transactions.
These ideas were forward-thinking in 2021, envisioning a shift away from the centralized giants dominating social media at the time. While Ulbricht didn’t specifically address advertising protocols, his framework for decentralization and user empowerment extends naturally to other domains, like NextBlock’s open-source offering: the PROMO Protocol.
NextBlock’s Implementation of PROMO Protocol
The PROMO Protocol powers NextBlock's Billboard app, a decentralized advertising protocol built on Nostr, a simple, open protocol for decentralized communication. The PROMO Protocol reimagines advertising by: * Empowering People: Individuals set their own ad prices (e.g., 500 sats/minute), giving them direct control over how their attention or space is monetized. * Marketplace Dynamics: Advertisers set budgets and maximum bids, competing within a decentralized system where a 20% service fee ensures operational sustainability. * Open-Source Flexibility: As an open-source protocol, it allows multiple developers to create interfaces or apps on top of it, avoiding the single-platform bottleneck Ulbricht critiqued. * Secure Payments: Using Strike Integration with Bitcoin Lightning Network, NextBlock enables bot-resistant and intermediary-free transactions, aligning value transfer with each person's control.
This structure decentralizes advertising in a way that mirrors Ulbricht’s broader vision for social systems, with aligned principles showing a specific use case: monetizing attention on Nostr.
Aligned Principles
Ulbricht’s 2021 article didn’t explicitly predict the PROMO Protocol, but its foundational concepts align remarkably well with NextBlock's implementation the protocol’s design: * Autonomy Over Value: Ulbricht argued that users should control their content and its economic benefits. In the PROMO Protocol, people dictate ad pricing, directly capturing the value of their participation. Whether it’s their time, influence, or digital space, rather than ceding it to a centralized ad network. * Ecosystem of Providers: Ulbricht envisioned multiple providers replacing a single platform. The PROMO Protocol’s open-source nature invites a similar diversity: anyone can build interfaces or tools on top of it, creating a competitive, decentralized advertising ecosystem rather than a walled garden. * Decentralized Transactions: Ulbricht’s DSP implied decentralized mechanisms for value exchange. NextBlock delivers this through the Bitcoin Lightning Network, ensuring that payments for ads are secure, instantaneous and final, a practical realization of Ulbricht’s call for user-controlled value flows. * Privacy and Control: While Ulbricht emphasized privacy in social interactions, the PROMO Protocol is public by default. Individuals are fully aware of all data that they generate since all Nostr messages are signed. All participants interact directly via Nostr.
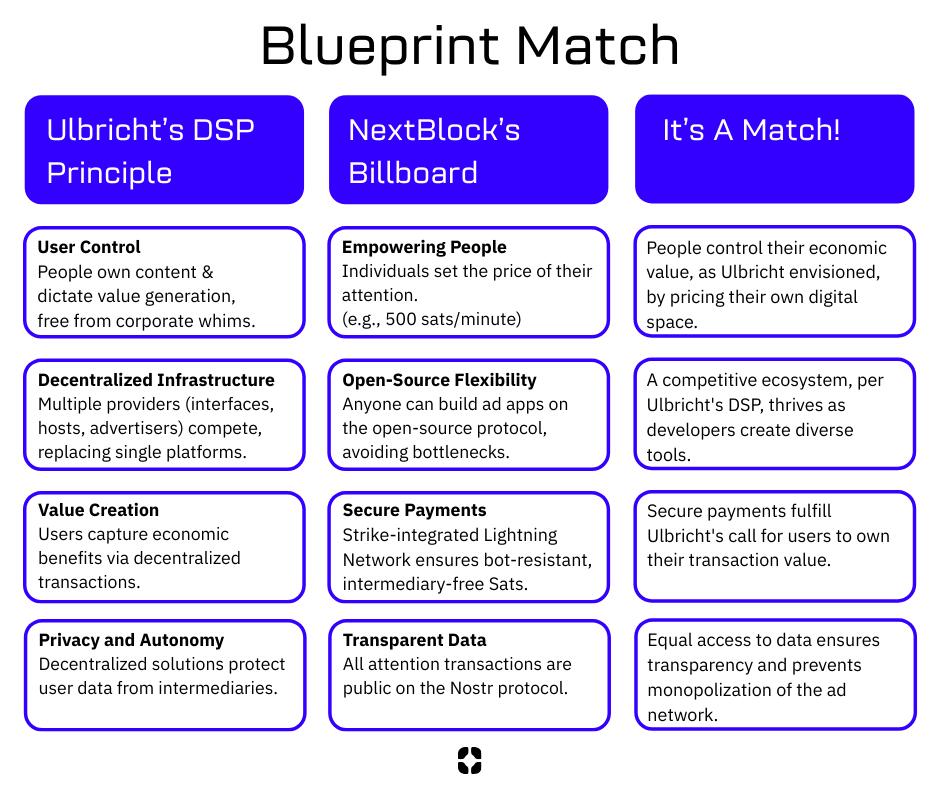 [Blueprint Match, source NextBlock]
[Blueprint Match, source NextBlock]
Who We Are
NextBlock is a US-based new media company reimagining digital ads for a decentralized future. Our founders, software and strategy experts, were hobbyist podcasters struggling to promote their work online without gaming the system. That sparked an idea: using new tech like Nostr and Bitcoin to build a decentralized attention market for people who value control and businesses seeking real connections.
Our first product, Billboard, is launching this June.
Open for All
Our model’s open-source! Check out the PROMO Protocol, built for promotion and attention trading. Anyone can join this decentralized ad network. Run your own billboard or use ours. This is a growing ecosystem for a new ad economy.
Our Vision
NextBlock wants to help build a new decentralized internet. Our revolutionary and transparent business model will bring honest revenue to companies hosting valuable digital spaces. Together, we will discover what our attention is really worth.
Read our Manifesto to learn more.
NextBlock is registered in Texas, USA.
-
 @ 318ebaba:9a262eae
2025-05-10 07:40:00
@ 318ebaba:9a262eae
2025-05-10 07:40:00When connecting to multiple relays in the Nostr protocol, users may encounter several challenges that can affect their overall experience. Here are some of the key issues:
Challenges of Connecting to Multiple Relays
-
Performance Issues: The lightweight design of Nostr relays can lead to performance bottlenecks, especially when many users are connected simultaneously. This can result in slow message delivery or even failures in posting messages if the relays are overwhelmed[1][2][32].
-
Reliability and Connectivity: Users may experience connectivity problems with certain relays, which can lead to inconsistent access to messages or delays in communication. If a relay goes offline or has connectivity issues, it can disrupt the flow of information, making it difficult for users to send or receive messages reliably[3][4][18].
-
Data Synchronization: As users connect to multiple relays, ensuring that data is synchronized across these relays can be challenging. Inconsistent data states may arise if different relays store messages differently or if there are delays in message propagation. This can lead to confusion about which messages have been sent or received[7][41].
-
Configuration Complexity: Managing connections to multiple relays requires a certain level of technical knowledge. Users need to configure their clients properly to connect to various relays, which can be daunting for those less familiar with the technology. Misconfigurations can lead to connection failures or suboptimal performance[4][21].
-
Spam and Quality Control: With the open nature of Nostr, some relays may be more susceptible to spam or low-quality content. Users connecting to multiple relays might encounter a higher volume of irrelevant or unwanted messages, which can detract from the overall user experience[6][32].
-
Security Concerns: When using multiple relays, users must be cautious about the security of their connections. Not all relays may implement the same level of security, and connecting to less secure relays could expose users to risks such as data interception or unauthorized access to their messages[26][27].
In summary, while connecting to multiple relays in Nostr offers benefits such as redundancy and improved access to information, users must navigate various challenges related to performance, reliability, configuration, and security. Addressing these issues is crucial for a smooth and effective experience on the Nostr network.
[1] https://forum.dfinity.org/t/introducing-replicatr-enhancing-nostr-with-internet-computer-integration/31861 [2] https://medium.com/coinmonks/a-deep-dive-into-nostr-clients-with-technical-insights-and-code-snippets-b1666bb11fac [3] https://nostr.com/nevent1qqsfvjvg73wxdn7mda28m704r2zv9lnzlcdgh8r0g52lfvy2wj7uw4czyq32rylmsmre84lhxdypy6jlu4dt3fxfwkq9a0p0lqdl9y8hsp0hur4fuw4 [4] https://www.reddit.com/r/nostr/comments/1e6nm68/new_nostream_relay_created_problems_with_publish/ [5] https://www.lynalden.com/the-power-of-nostr/ [6] https://bitcoinmagazine.com/technical/how-nostr-can-improve-bitcoin-privacy [7] https://barelybuggy.blog/2024/11/26/mostr-offline/ [8] https://github.com/scsibug/nostr-rs-relay/issues/126 [9] https://community.umbrel.com/t/nostr-relay-troubleshooting/17828 [10] https://research.dorahacks.io/2024/04/30/nostr-relay-incentive/ [11] https://community.start9.com/t/issue-confirming-nostr-relay/1682 [12] https://arxiv.org/html/2402.05709v1 [13] https://community.umbrel.com/t/nostr-relay-not-connecting/11401 [14] https://www.purplerelay.com/troubleshooting-common-issues-with-nostr-relay-server-a-users-guide/ [15] https://news.ycombinator.com/item?id=35694029 [16] https://substack.com/home/post/p-158872714?utm_campaign=post&utm_medium=web [17] https://stacker.news/items/142013 [18] https://www.reddit.com/r/nostr/comments/1h6admk/are_these_relays_working/ [19] https://news.ycombinator.com/item?id=33746360 [20] https://github.com/scsibug/nostr-rs-relay/issues/195 [21] https://www.purplerelay.com/how-to-run-a-nostr-relay-a-step-by-step-guide/ [22] https://denostr.medium.com/the-future-of-social-communication-nostrs-origins-and-the-next-destination-in-social-networking-27f0c901d7ae [23] https://nostr.com/nevent1qqsqwklh29cvf3z0skhh77xyqf3m53xkppcttf3c8nuc2jqteulfx0czyqcgr7epv9hha2v9afp99l5wl0ljna0zum59fzyhl9v8pgv5xlhf5ava642 [24] https://www.reddit.com/r/nostr/comments/15fyr6r/pervasive_private_key_sharing_seems_dangerous/ [25] https://whtwnd.com/agoracitizen.network/3l2fysaripd2q [26] https://ron.stoner.com/nostr_Security_and_Privacy/ [27] https://forums.puri.sm/t/about-what-is-nostr/20764 [28] https://github.com/nostr-protocol/nips/issues/107 [29] https://medium.com/@volodymyrpavlyshyn/security-features-of-nostr-a0276a22e815 [30] https://nostr.com/nevent1qqspd8fh3tplxtfhjpka3y3glzh63v3ygsdhacyq8dvyrnxtvl09lpczyr2v7dprke9lad2qk0svug55vxguqv7n3dwn9vm63u8n5n84znxjxedjf6c [31] https://nostr.com/nevent1qqs8e2su6n8m2xtg45qdjw7rdcq6w3g5guvt085h52qhg25wxn755sczyrh26kg89z95jqaz4xkex7kaw2t36twtc75vmrfx2k3p3jqvhfa8vzan82f [32] https://www.cointribune.com/en/nostr-et-la-censure-pourquoi-un-reseau-social-decentralise-est-essentiel-2/ [33] https://nostr.com/nevent1qqsv86d756zcw32x0zcvqmr924y5sltvwqud0dywny83ndee30zzrmczyrh26kg89z95jqaz4xkex7kaw2t36twtc75vmrfx2k3p3jqvhfa8vwpfv29 [34] https://github.com/nbd-wtf/nostr-tools/issues [35] https://www.voltage.cloud/blog/the-growth-of-nostr-the-era-of-decentralization [36] https://medium.com/@BingVentures/status-quo-challenges-and-prospect-of-decentralized-social-networks-18f9584f2e8d [37] https://www.reddit.com/r/RedditAlternatives/comments/14s8ao4/greetings_im_here_to_tell_you_about_nostr_a/ [38] https://bitcoinmagazine.com/culture/nostr-the-importance-of-censorship-resistant-communication-for-innovation-and-human-progress- [39] https://github.com/mayneyao/eidos/issues/129 [40] https://www.reddit.com/r/nostr/comments/115a8et/data_duplication_and_distribution_in_nostr_relays/ [41] https://github.com/open-nostr/nostar [42] https://nostr.com/nevent1qqsryg8zuc9rdwldat385al24mdt56wanc6g6hfymy8l9tgtmzsc4nspzemhxue69uhhyetvv9ujuurjd9kkzmpwdejhg85cx73 [43] https://ckbcn.xlog.app/Nostr-sheng-tai-fa-zhan-xian-zhuang-ji-wen-ti?locale=en [44] https://nostr.com/naddr1qqc92mnvda3kk6twvuk5ummnw3ez6ued2phhgetww35kzmpdwa5hg6pdfehhgetyv43kktt08p5hscnkqgsr7acdvhf6we9fch94qwhpy0nza36e3tgrtkpku25ppuu80f69kfqrqsqqqa28aknkml
-
-
 @ 1893da11:a9bd4471
2025-05-08 14:42:20
@ 1893da11:a9bd4471
2025-05-08 14:42:20Introduction: The Challenge of Bitcoin-Secured Loans
Bitcoin holders often face a dilemma: they need liquidity but don't want to sell their assets, potentially missing out on future gains or triggering taxable events. Bitcoin-secured loans offer a solution, allowing users to borrow cash (like digital dollars) using their Bitcoin as collateral. However, the current landscape is fraught with challenges. Many existing solutions require users to trust centralized entities or involve complex mechanisms like wrapping Bitcoin, exposing them to significant risks:
- Custodial Risk: Handing over your Bitcoin to a third party means trusting they won't lose it, misuse it, or become insolvent. Billions have been lost this way.
- Smart Contract Risk: Platforms built on chains like Ethereum rely on complex smart contracts, which can contain bugs or vulnerabilities exploitable by hackers.
- Oracle Risk: Loan systems need reliable price feeds (oracles) to manage collateral. Centralized or manipulatable oracles can lead to unfair liquidations.
- Privacy Risk: Loan details and transactions are often publicly visible on the blockchain.
- Complexity and Cost: Existing processes can be slow, require extensive documentation, and involve high fees.
There's a clear need for a better way – one that is simple, reliable, and minimizes trust. This is where the Lava Loans Protocol comes in.
What is Lava Loans?
In simple terms, Lava Loans provides a way to borrow digital dollars using your native Bitcoin as collateral, directly from your own vault. It's designed to be:
- Simple & Fast: Get a loan in seconds with minimal questions asked.
- Low-Cost & Flexible: Offers competitive rates, dynamic fee structures, and allows borrowing any amount.
- Reliable & Trust-Minimized: Leverages Bitcoin's own capabilities to reduce reliance on intermediaries and enhance security.
How Lava Loans Addresses the Risks
Lava tackles the common pitfalls of crypto loans head-on:
- Eliminating Custodial Risk: Instead of transferring your Bitcoin to a custodian or wrapping it, Lava uses native Bitcoin locked directly on the Bitcoin network within a special type of contract. This prevents rehypothecation and loss through hacks or confiscation.
- Minimizing Smart Contract Risk: Lava utilizes Bitcoin smart contracts, also known as Discreet Log Contracts (DLCs). These are designed to be less complex and more secure than many general-purpose smart contracts, with outcomes pre-defined and formally verified.
- Reducing Oracle Risk: Users choose their own off-chain, blinded oracles (called Sibyls) for price data, with enhanced redundancy to ensure reliability. Off-chain attestations avoid high fees and miner manipulation risks associated with on-chain oracles. Blinded oracles provide price data without knowing the specific contract they influence, preventing targeted attacks.
- Enhancing Privacy: Because DLCs operate differently from typical public smart contracts, the details of the loan contract are not broadcast publicly on the Bitcoin blockchain.
- Trustless Initiation & Repayment: Atomic swaps ensure that collateral only moves to the contract once the loan is received, and collateral is automatically returned upon verified repayment.
The Magic Ingredients: DLCs and Sibyls Oracles
Two core technologies make Lava Loans unique:
-
Discreet Log Contracts (DLCs): Think of a DLC as a pre-programmed Bitcoin transaction agreed upon by the borrower and lender. Before the loan starts, they define all possible outcomes (e.g., repayment, liquidation at a specific price, expiry) and create encrypted signatures for each. The Bitcoin collateral is locked in a multisig output controlled by these pre-signed transactions. Only the conditions agreed upon (verified by oracle signatures) can unlock the funds according to the pre-defined rules. This offers:
- Security: Formally verified, pre-defined outcomes minimize bug risk.
- Privacy: Contract details remain off-chain.
- Scalability: Minimal on-chain footprint as execution logic is off-chain.
- Customization: Users can choose their own oracles and LTV thresholds.
-
Sibyls Oracles: These are the independent price feed providers for Lava. Key characteristics include:
- Off-Chain: Attestations happen off-chain, avoiding blockchain fees and manipulation.
- User-Chosen: Borrowers select the oracles they trust for each loan.
- Blinded: Oracles provide signed price data without knowing the specific DLC it applies to, enhancing security.
- Redundant: Multiple oracles can be configured to provide fallback price feeds, reducing the risk of oracle failure.
System Overview
Here's a high-level look at the components involved in the Lava Loans ecosystem:
[ Borrower ] --(locks Bitcoin)--> [ DLC Contract (Bitcoin) ] [ Lender ] --(sends stablecoins)--> [ Alt-Chain Contract (Solana) ] [ Oracles ] --(provides price)--> [ DLC Contract (Bitcoin) ] [ Borrower ] --(repays loan)--> [ Alt-Chain Contract (Solana) ] [ Lender ] --(claims collateral)--> [ DLC Contract (Bitcoin) ]The Lava Loan Lifecycle
A loan progresses through several states:
- Initialized: A trustless atomic swap occurs. The borrower locks Bitcoin collateral into the DLC on the Bitcoin network, and the lender locks the loan capital (e.g., digital dollars on a network like Solana using HTLCs) which the borrower then claims.
- Active: The collateral is secured in the DLC, and the borrower has the loan capital. The Lava Protocol monitors the loan-to-value (LTV) ratio using price data from the chosen Sibyls oracles, with customizable LTV thresholds for greater flexibility.
- Terminated: The loan concludes in one of several ways:
- Repaid: The borrower repays the loan capital plus interest on the loan asset network, with dynamic fees adjusting based on network conditions. Upon verification, the DLC automatically releases the Bitcoin collateral back to the borrower.
- Liquidated: If the Bitcoin price drops and the LTV reaches a pre-determined threshold (now more flexible to avoid premature liquidations), the DLC automatically releases the collateral to the lender.
- Expired: If the loan term ends before repayment, the DLC releases an amount equivalent to the principal plus interest to the lender, and the remaining collateral is returned to the borrower.
- Fail-safe: In rare cases of unresponsive oracles, redundant Sibyls oracles and built-in mechanisms ensure collateral is not permanently lost.
Loan Process Sequence
The following diagram illustrates the typical sequence of events in a Lava Loan:
1. Borrower --> DLC: Create loan contract with collateral 2. Lender --> Alt-Chain: Fund loan with stablecoins 3. Borrower --> Alt-Chain: Receive and use stablecoins 4. (If repayment) 4a. Borrower --> Alt-Chain: Repay loan 4b. Lender --> Alt-Chain: Confirm repayment 4c. Borrower --> DLC: Claim collateral 5. (If liquidation) 5a. Oracle --> DLC: Provide price attestation 5b. Lender --> DLC: Claim collateral 6. (If expiry) 6a. Borrower/Lender --> DLC: Split collateralLava Loans vs. Other Bitcoin Lending Platforms: A Quick Comparison
How does Lava stack up against typical DeFi lending protocols and other Bitcoin lending platforms like Unchained, Strike, and Coinbase?
| Feature | Lava Loans (Bitcoin) | Typical Ethereum DeFi | Unchained | Strike | Coinbase | | :------------------- | :---------------------------------------------------- | :-------------------------------------------------------- | :---------------------------------------------------- | :---------------------------------------------------- | :---------------------------------------------------- | | Collateral | Native Bitcoin | Often Wrapped Bitcoin (wBTC) or other assets | Native Bitcoin | Native Bitcoin | Native Bitcoin | | Contract Type | Discreet Log Contracts (DLCs) - Pre-agreed, Private | Smart Contracts - Public, Complex, Run on EVM | 2/3 Multisig Vaults | Custodial Contracts | Custodial Contracts | | Security | Aims for higher security via simpler, pre-set DLCs | Can be complex, potential for bugs/exploits | Secure via multisig, but relies on key holders | Custodial, less transparent | Custodial, less transparent | | Privacy | Higher privacy (contract details off-chain) | Lower privacy (contract interactions often public) | Moderate privacy (multisig details on-chain) | Lower privacy (custodial model) | Lower privacy (custodial model) | | Oracles | User-chosen, Off-chain, Blinded (Sibyls) | Often On-chain, potentially manipulatable | Not applicable (manual monitoring) | Centralized oracles | Centralized oracles | | Trust | Designed to minimize trust in intermediaries | Often requires trust in custodians, bridges, or protocols | Moderate trust (key holders could collude) | Higher trust (custodial, opaque practices) | Higher trust (custodial, opaque practices) | | Rehypothecation | No rehypothecation, verifiable on-chain via DLCs | Possible, depends on protocol | No rehypothecation, secured by multisig | Opaque, likely rehypothecated | Opaque, likely rehypothecated | | Interest Rates | Competitive, typically lower due to non-custodial model | Varies, often 5-10% for wBTC loans | 11-14% for non-rehypothecated loans | 12-13% (implies rehypothecation) | ~5-6% (implies rehypothecation) |
Lava leverages Bitcoin’s native capabilities and a specific oracle design to prioritize security, privacy, and trust minimization. Unlike Unchained, which uses a 2/3 multisig where two key holders could potentially collude, Lava’s DLCs ensure cryptographic proof of non-rehypothecation, verifiable on-chain in real time. Strike and Coinbase, being custodial, lack transparency about rehypothecation practices, with market rates suggesting they rehypothecate collateral. The v3 protocol introduces dynamic fee adjustments and more flexible LTV thresholds, reducing premature liquidations and optimizing costs based on network conditions.
Conclusion
Lava Loans presents a compelling option for those seeking liquidity against their Bitcoin holdings without sacrificing security or control. By utilizing Discreet Log Contracts, a user-centric, blinded oracle system (Sibyls) with enhanced redundancy, and new features like dynamic fees and flexible LTV thresholds, Lava provides a simple, reliable, and trust-minimized borrowing experience. These advancements directly address the major pain points found in many existing centralized and decentralized lending platforms.
References
- Maredia, Shehzan. "Lava Loans". Lava Blog, April 9, 2025. https://www.lava.xyz/blog/lava-loans
- https://github.com/lava-xyz/loans-paper/blob/main/loans_v3.pdf
- https://github.com/lava-xyz/sibyls