-
 @ a296b972:e5a7a2e8
2025-05-12 16:52:30
@ a296b972:e5a7a2e8
2025-05-12 16:52:30Wo sind der 1. Stock, das Erdgeschoss und der Keller? Das Dach ist noch zu bauen. Das Haus zum unerklärlichen Krieg ist unfertig. Der Bau wurde schon viel früher begonnen, aber die westlichen Medien behaupten das Gegenteil oder verschweigen es. Eine Vorgeschichte darf es nicht geben.
Am Ukraine-Krieg sieht man, dass ein Konflikt, der entgegen den Behauptungen der Propaganda-Maschine nicht erst im Februar 2022 angefangen hat, wie lange es dauert, bis wieder Verhältnisse zustande kommen, die eine Befriedung ermöglichen. Das Ringen darum ist hoffentlich endlich in die Zielgerade eingelaufen und man findet besser gestern als heute eine Lösung. So viele Menschenleben auf beiden Seiten hat dieser Wahnsinn bislang gekostet. Am Ende, wofür? Die Verwirrung bleibt bis zuletzt, denn einerseits treibt der US-amerikanische Präsident die Friedensbemühungen maßgeblich voran, andererseits werden von US-amerikanischer Seite mutmaßlich die Waffenlieferungen fortgesetzt und Starlink nicht abgeschaltet, was erheblich zum abrupten Beenden des sinnlosen Sterbens beitragen würde.
Verträge sind zu erfüllen? Sicherung der US-amerikanischen Interessen? Druckmittel auf Russland? Und Europa? Europa, vor allem Deutschland, Frankreich und Großbritannien geben weiterhin den Geisterfahrer und haben immer noch nicht mitbekommen, dass sie in der Beilegung des Ukraine-Kriegs nicht das geringste zu sagen haben. Sie spielen sich aber auf, als hätten sie und machen „einen auf dicke Hose“. Murmeln werden als Eier verkauft.
Etwas aus dem Fokus der Neuen Medien gerät dabei der immer noch wütende Krieg im Gaza-Streifen mit einer israelischen Planier-Raupe, dessen Vorgeschichte noch länger ist, als die, die zum Ukraine-Krieg geführt hat. Rund 80 Jahre, aber auch hier eigentlich noch länger. Man kann sich vorstellen, wie lange es hier dauern wird, bis sich sichere, friedliche Verhältnisse einstellen können.
Wer kann sicher sein, wer nimmt sich das Recht heraus zu behaupten, wer entscheidet darüber, dass sich Zustände, wie im 3. Reich, die Verfolgung und Vernichtung einer Minderheit, damals die Juden, nicht wiederholen kann? Seitdem das geschehen ist, hat sich der Großteil der Menschheit keinen Millimeter weiterentwickelt.
Wenn gerade Deutsche Anzeichen für eine Wiederholung dieser tief-dunklen Zeit zu erkennen glauben, derzeit in dem, wie der israelische Staat mit dem Gaza-Streifen verfährt, dann ist das keine Verharmlosung der Gräueltaten im 3. Reich, sondern der Beweis dafür, dass es doch einige gibt, die aus der Geschichte gelernt haben, und die der Meinung sind, dass sich so etwas niemals mehr wiederholen darf.
Um auf einen Genozid hinzuweisen, muss jeder Vergleich möglich und erlaubt sein. Es geht um eine Mehrzahl von Menschen, von Familien, die einfach nur in Frieden leben wollen! Ungeachtet der Tatsache, dass es auf beiden Seiten Kräfte gibt, die das nicht interessiert.
Besonders tragisch wird es, wenn dieser Genozid augenscheinlich ausgerechnet von denen ausgeht, die selbst so schrecklich davon betroffen waren.
Wie kann sich der deutsche Staat erdreisten, diejenigen als Anti-Semiten zu bezeichnen, die hier Merkmale eines Genozids zu erkennen glauben und versuchen, diese kritischen Stimmen zu unterdrücken, „nur“, weil es sich um den Staat Israel handelt, der hier als Täter infrage kommt. Auch der Staat Israel hat keinen Freibrief, die Bevölkerung im Gaza-Streifen nach seinen Vorstellungen und Überzeugungen abzurasieren.
Ein Genozid ist ein Genozid, egal von welcher Regierung eines Landes er begangen wird.
Der Staat Israel ist keine Ausnahme! Im Gegenteil. Aufgrund der Erfahrung seines Volkes müsste es die Menschlichkeit gebieten, dass derartiger Völkermord nie wieder geschieht.
Weiter müsste der Begriff Anti-Semitismus einmal genau unter die Lupe genommen werden, was wer aus welchen Gründen darunter versteht. Man kann den Eindruck gewinnen, dass dieser Begriff vor allem als Totschlagargument verwendet wird, um kritische Stimmen mundtot zu machen. Besonders bei diesem heiklen Thema wäre absolute Akkuratesse dringend notwendig.
Es ist die Pflicht eines jeden, der Kritik an den Zuständen üben will, nicht zu verallgemeinern.
Nicht alle israelischen Staatsbürger sind Netanjahu-Anhänger (das zeigen die Demonstrationen), nicht alle Juden sind Zionisten, nicht einmal alle Zionisten sind Juden.
Und sicher sind auf der Gaza-Seite ebenfalls nicht nur „Engel“ unterwegs!
Beide Lager haben rund 80 Jahre Zeit gehabt, den gegenseitigen Hass durch gegenseitige Provokationen aufzubauen und ihn immer wieder sich entladen zu lassen.
Dieser unermessliche Hass kann nur über Generationen hinweg wieder abgebaut werden.
Wenn es jemals eine ernste Absicht gegeben hätte, eine 2-Staaten-Lösung zu realisieren, wäre diese schon längst in die Tat umgesetzt worden. Wenn jedoch der politische Wille dazu fehlt, vor allem auf der Seite des Stärkeren, passiert gar nichts. Und der fehlt jetzt schon seit rund 80 Jahren.
Maßgeblich durch die Briten ist der Staat Israel künstlich entstanden. Die Ableitung der Nutznießer auf einen Gebietsanspruch aus einem Glauben heraus, ist einmalig.
In dem nicht natürlich entstandenen, sondern künstlich geschaffenen Staatsgebilde liegt möglicherweise die Wurzel allen Übels, die von langer Hand, spätestens durch die Balfour-Deklaration im Jahre 1917 ihren Anfang genommen hat.
Man hat nun Jahrzehnte lang Zeit gehabt, zu beobachten, dass dieses Konstrukt ein sicheres Leben und eine Garantie für friedliche Verhältnisse aller nicht zustande gebracht hat. Schmerzliche Erfahrungen auf beiden Seiten haben bislang nicht dazu geführt, dass man zu der Einsicht gekommen wäre, dass man sich möglicherweise auf dem Holzweg befindet.
Die verfeindeten Lager müssten sich, neutral moderiert (welcher Staat, welcher Mensch ist heute noch neutral, oder zumindest kein Interessenvertreter?), zusammensetzen und sich in sicher nicht einfachen, langwierigen, zähen Gesprächen und Verhandlungen über die Neugründung eines gemeinsamen Staates für alle Beteiligten ernsthaft nachdenken, solange, bis es zu einer Einigung gekommen wäre, die für alle Beteiligten akzeptabel ist. Das Ergebnis, eine gemeinsame Staatenlösung, müsste das erklärte Ziel sein und wenn es noch so lange dauern würde.
Das Mitspracherecht müsste nach Bevölkerungsanteil in einem gerechten Verhältnis festgelegt werden. So müssten kleinere Anteile verhältnismäßig mehr Stimmanteile haben, als der größere Anteil, um zu möglichst für alle gerechten Entscheidungen zu gelangen, die alle Beteiligten mittragen könnten. Ein Vorankommen wäre nur durch Vernunft, nicht durch Starrsinn möglich.
Aufgrund der hitzigen Mentalität aller Beteiligten müssten beide Lager auf Gedeih und Verderb voneinander abhängig gemacht werden, sodass ein friedliches Zusammenraufen immer wieder nötig wäre, weil niemand in der Lage wäre, die Oberhand zu gewinnen.
Es müssten gegenseitige Abhängigkeiten geschaffen werden. So könnten zum Beispiel Lieferungen von Lebensmitteln, Wasser, Energie (Israel) usw. mit der Hoheit über die noch zu erschließenden Gasfelder (Gaza) vor Gaza „verrechnet“ werden, ohne, dass die USA oder sonst wer die Finger im Spiel haben.
Bei derartigen gegenseitigen Abhängigkeiten würde man sich schon zusammenraufen.
Das alles setzt voraus, dass der Mensch an sich seine menschlichen Schwächen unter Kontrolle bringen würde. Hierzu können Machtstreben, Geldgier, Rechthaberei, Überheblichkeit, Ideologien, Ansprüche aus einem Glauben heraus usw. gezählt werden.
Jerusalem müsste einen Sonderstatus erhalten und die Verwaltung müsste unter den drei Weltreligionen aufgeteilt werden. Jerusalem könnte im „Kleinen“ ein Beispiel dafür sein, wie der gesamte neue Staat im „Großen“ funktioniert. Und möglicherweise würde er so in der Tat funktionieren.
Für viele mag das alles vielleicht naiv oder sogar absurd klingen. Zur Herstellung von Frieden, Frieden in dem jede Mutter, gleich welcher Religion sie angehört, ihre Kinder in Sicherheit aufwachsen sehen kann, muss jede Überlegung und Idee, wie ein friedliches Miteinander realisiert werden kann, erlaubt sein zu denken und auch auszusprechen.
Eines ist sicher. So, wie die Verhältnisse in der Vergangenheit gestaltet wurden, hat die Realität eindeutig gezeigt, dass es so auf gar keinen Fall funktioniert. Also, warum nicht einfach einmal das Gehirn durchblasen, alte, überkommene Überzeugungen loswerden und endlich einmal etwas Neues denken?
Und wer jetzt immer noch sagt, das wäre eine Delegitimierung des Staates Israel, der sollte seine Gehirnwindungen einmal zur Inspektion bringen. Der Mensch, egal welcher Couleur und welcher Religion steht hier im Mittelpunkt. Im Mittelpunkt stehen Überlegungen, wie ein friedliches Miteinander möglich sein könnte. Falls sich herausstellt, dass das eine Utopie ist, auch gut, aber immerhin sind sich Gedanken gemacht worden, die von den eingefahrenen, zu nichts außer Elend führenden Entscheidungen abweichen. Und wenn es nur zur Anregung für andere Ideen dient, dann wäre schon viel getan. Und das ist weder anti-semitisch, noch anti-israelisch, noch anti-christlich, noch anti-moslemisch, noch anti-sonst wie, sondern vor allem ein Appell an die Vernunft, zu der der Mensch schließlich auch begabt ist.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von Georg Ohrweh)
-
 @ 51faaa77:2c26615b
2025-05-12 17:34:37
@ 51faaa77:2c26615b
2025-05-12 17:34:37My goal is to share a concise list of questions about OP_RETURN limits that we've answered on Stacker News, as the original thread has become unwieldy with over 200 comments. We began compiling this list about a week ago. I've frequently shared individual links and received very positive feedback. I hope this resource helps us work from a common set of facts and reduces misinformation. I hope you find this as a valuable resource.
I'll list the questions in order of activity and tips received. I've removed duplicates, rephrased some statements as questions, and ignored completely irrelevant questions.
- Users should be given clear configurable options to decide what's in their mempool, why were these options taken away? link
- Won't spammers abuse large OP_RETURNs to bloat the blockchain and make IBD take longer? link
- A similar PR was proposed by Peter Todd 2 years ago, why was it rejected then? What has changed since then, why would this get approved now? link
- Shouldn't we be fighting spam, why are we making policies less strict, shouldn't we be making them more strict? link
- How would someone get around the standardness policy currently for OP_RETURN size? link
- What does "standardness mean" in reference to OP_RETURNs? link
- Will more than 1 OP_RETURN per transaction be possible if this PR gets merged? link
- What are the current OP_RETURN limits and what restrictions are being lifted? link
- Are current relay and mempool policies effective for filtering out spam transactions? link
- Is it true that this type of update could affect Bitcoin's decentralization? link
- Is it possible to stop the abuse of payment outputs (i.e., bare multisig, fake pubkeys, and fake pubkey hashes) that are used to embed data, thereby creating unprunable UTXOs that bloat the UTXO set? link
- What was the main reason /concern to add this PR? ... What will happen if we do nothing? link
- If OP_RETURN still cannot stop all the garbage, why is so important to remove it? Does it affect future development / improvements for LN? link
- What will be the worst case scenario if users still could set their own limits for OP_RETURN? link
- Shouldn't we debate the controversy of this PR on Github since it's where the code gets merged to make these changes? link
- What does it mean when someone says "Fix the Filters"? link
- Will this open the flood gates and drown out all legitimate onchain activity? link
- What can we do to stop spam at the consensus layer of Bitcoin? link
- Will Taproot wizards and other spam companies and projects start using OP_RETURN to put jpegs on the blockchain? link
- If we prevent these transaction from going into our mempools doesn't that prevent or delay these spam transactions from being mined therefore discouraging the spammers? link
- Is it possible to stop abuse of witness data? If so, how? (i.e ordinal theory inscriptions, "jpegs"). link
- Is there any conflict of interest with Bitcoin Core and companies like Citrea, in ref to this PR? link
- Is there any estimation on how much would this affect fees for the average user, considering external projects (like Citrea) using it? Any possibility that this could saturate the mempool and boost fees beyond reasonable? link
- Was this PR initially proposed because of Citrea BitVM needs? If so don't they only need a slight bump in OP_RETURN size, why is it being proposed to make the size unrestricted? link
- What makes a UTXO unprunable? Which projects are making unprunable UTXOs? link
- Why would a spammer use OP_RETURN if it's cheaper to use Witness data to store arbitrary data? link
- Won't large OP_RETURNs allow people to spam the mempool with 100kb transactions and mess up bitcoin for everyone by bloating the mempool and not allowing legitimate transactions in the mempool? link
- If relaxing op_return standardness limit seeks to make 'spam' prunable, then what are proponents of this change assuming about the long-term feasibility of running a 'full' (unpruned) bitcoin node? link
- Is allowing standardness for larger OP_RETURNs a slippery slope? If we allow this won't we continue to allow things that make bitcoin less for money and more for arbitrary data? link
- Won't removing the OP_RETURN cap reduce fee market pressure by allowing senders to consolidate arbitrary data into a single transaction? link
- Could this PR be the beginning of reducing other mempool restrictions? link
- Culture is what protects Bitcoin from external forces, shouldn't non-technical arguments be valid when considering these types of changes? link
- What's the difference between UTXO set, mempool, and blockchain, and how do larger OP_RETURN or witness data affect node resource usage? link
- What is the difference in defining a transaction as valid versus defining a transaction as standard and why do we need this difference? link
- If you're happy with your viewpoint on consensus and mempool rules, is not upgrading Bitcoin Core until it makes sense to you a valid action to take right now? link
- Why didn't this PR get a BIP number? link
- Why is core rushing this change? link
- If there will be a hard fork resulted from this PR (split chain like in 2017), what will happen with existing LN channels? Will exist on both chains with 2 LNs? link
- Isn't this all moot in a (almost guaranteed) future where fees are very high? link
- What is this controversy about, and what is it really about? link
originally posted at https://stacker.news/items/978404
-
 @ c9badfea:610f861a
2025-05-12 16:29:32
@ c9badfea:610f861a
2025-05-12 16:29:32- Install Organic Maps
- Launch the app and download the World Map first
- Tap the ☰ at the bottom, then select Download Maps, and tap the + icon
- Download maps by tapping ⤓ next to your desired region
- Return to the main screen and tap 🔍 to search for your destination
- Enjoy navigating offline
ℹ️ Note that Organic Maps does not provide live traffic updates
-
 @ 6be5cc06:5259daf0
2025-05-12 14:50:36
@ 6be5cc06:5259daf0
2025-05-12 14:50:36A posição do libertário que rejeita o cristianismo padece de sérias incoerências lógicas, históricas e filosóficas. Ao renegar as bases espirituais e culturais que tornaram possível o próprio ideal libertário, tal posição demonstra ser, ao mesmo tempo, autofágica e irracional. É o caso de alguém que se gloria dos frutos de uma árvore que corta pela raiz.
I. Fundamento histórico: a civilização da liberdade é cristã
Não foi o secularismo moderno, nem o paganismo antigo, que ergueram as instituições que protegem a dignidade da pessoa humana e os limites ao poder. Desde os primeiros séculos, a Igreja resistiu ao culto estatal romano, afirmando a soberania de Deus sobre os Césares — "Mais importa obedecer a Deus que aos homens" (Atos 5,29).
Foi o cristianismo que:
-
Fundou universidades livres, onde o saber era buscado sob o primado da verdade;
-
Defendeu a lei natural como fundamento do direito — uma doutrina que protege o indivíduo contra tiranias;
-
Resgatou e aprofundou o conceito de pessoa, dotada de razão e livre-arbítrio, imagem de Deus, e, portanto, inalienavelmente digna e responsável.
Em momentos-chave da história, como nas disputas entre papado e império, nas resistências contra absolutismos, e na fundação do direito internacional por Francisco de Vitoria e a Escola de Salamanca, foi o cristianismo quem freou o poder estatal em nome de princípios superiores. A tradição cristã foi frequentemente o principal obstáculo à tirania, não seu aliado.
Negar isso é amputar a própria genealogia da liberdade ocidental.
Uma das chaves do cristianismo para a construção dessa civilização da liberdade foi a exaltação do individualismo. Ao afirmar que o ser humano é feito à imagem de Deus e que sua salvação é uma escolha pessoal, o cristianismo colocou o indivíduo no centro da moralidade e da liberdade. Diferente dos gregos, cuja ética era voltada para a polis e a cidade-estado, o cristianismo reafirma a suprema importância do indivíduo, com sua capacidade de escolha moral, responsabilidade pessoal e dignidade intrínseca. Esse princípio, mais do que qualquer outra religião, foi o alicerce do desenvolvimento da liberdade individual e da autonomia, valores que sustentam a civilização ocidental.
A ética grega, na melhor das hipóteses, descreve a ordem natural — mas não consegue justificar por que essa ordem deveria obrigar a vontade humana. Um Logos impessoal não tem autoridade moral. Uma ordem cósmica sem um Legislador é apenas um dado de fato, não uma norma vinculante. A vontade pode rebelar-se contra o telos — e sem um Deus justo, que ordena a natureza à perfeição, não há razão última para não o fazer.
A cultura grega teve uma influência indiscutível sobre o desenvolvimento da civilização ocidental, mas o cristianismo não só absorveu o que havia de bom na cultura grega, como também elevou e completou esses aspectos. O cristianismo, ao afirmar que todos os homens são feitos à imagem e semelhança de Deus e têm dignidade intrínseca, levou a uma noção de igualdade moral e liberdade que transcende as limitações da pólis grega.
II. Falsa dicotomia: fé e liberdade não são opostas
Com frequência equiparam a religião à coerção e à obediência cega. Mas isso é um equívoco: o cristianismo não se impõe pela força, mas apela à consciência. O próprio Deus, em sua relação com a criatura racional, respeita sua liberdade. Como ensina a Escritura:
"Se alguém quiser vir após mim..." (Mt 16,24);
"Eis que estou à porta e bato. Se alguém ouvir a minha voz e abrir a porta, entrarei em sua casa e cearei com ele." (Ap 3,20);
"Assim falai, e assim procedei, como devendo ser julgados pela lei da liberdade." (Tiago 2,12).A adesão à fé deve ser livre, voluntária e racional, pois sem liberdade não há verdadeiro mérito, nem amor genuíno. Isso é mais compatível com o princípio de não agressão do que qualquer utopia secular. Ora, o núcleo do evangelho é voluntarista: salvação pessoal, conversão interior, caridade.
Ninguém deve ser forçado, contra sua vontade, a abraçar a fé, pois o ato de fé é por sua natureza voluntário (Dignitatis Humanae; CDC, cân. 748,2)
Se algum Estado usa da força para impor o cristianismo, afirmar que o cristianismo causou as coerções é tão equivocado quanto dizer que a propriedade privada causa o comunismo; é uma inversão da realidade, pois o comunismo surge precisamente da violação da propriedade. Portanto, a fé forçada é inválida em si mesma, pois viola a natureza do ato de crer, que deve ser livre.
III. Fundamento moral: sem transcendência, o libertarianismo flutua no vácuo
O libertário anticristão busca defender princípios objetivos — como a inviolabilidade do indivíduo e a ilegitimidade da agressão — sem um fundamento transcendente que lhes dê validade universal. Por que a agressão é errada? Por que alguém tem direito à vida, à liberdade, à propriedade? Sem uma explicação transcendental, as respostas para tais perguntas se tornam apenas opiniões ou convenções, não obrigações morais vinculantes. Se a moralidade é puramente humana, então os direitos podem ser modificados ou ignorados conforme a vontade da sociedade. O conceito de direitos naturais, tão caro ao libertarianismo, precisa de um solo metafísico que justifique sua universalidade e imutabilidade. Caso contrário, eles podem ser tratados apenas como acordos utilitários temporários ou preferências culturais, sem qualquer obrigatoriedade para todos os seres humanos em todas as circunstâncias.
Pensadores libertários seculares, como Ayn Rand e Murray Rothbard, tentaram ancorar os direitos naturais na razão humana ou na natureza do homem. Rand baseia sua ética no egoísmo racional, enquanto Rothbard apela à lei natural. Embora essas abordagens busquem objetividade, elas carecem de uma resposta definitiva para por que a razão ou a natureza humana obrigam moralmente todos os indivíduos. Sem um fundamento transcendente, suas concepções permanecem vulneráveis a interpretações subjetivas ou a cálculos utilitários.
Aqui, o cristianismo oferece uma explicação sólida e transcendental que fundamenta os direitos naturais. A visão cristã de que o ser humano foi criado à imagem e semelhança de Deus confere à pessoa uma dignidade intrínseca, imutável e universal. Essa dignidade não depende de fatores externos, como consenso social ou poder político, mas é uma característica inerente ao ser humano pela sua criação divina. A partir dessa perspectiva teológica, torna-se possível afirmar com base sólida que os direitos naturais são dados por Deus e, portanto, são universais e vinculantes.
O cristianismo também é a base de um sistema moral que distingue claramente justiça de legalidade. O Estado pode criar leis, mas isso não significa que essas leis sejam justas. A justiça, sob a ótica cristã, é uma expressão da ordem moral objetiva, algo que transcende as leis humanas e é definido pela vontade divina. Por isso, o libertarianismo cristão vê a agressão como uma violação de uma ordem moral objetiva, e não apenas uma violação de uma convenção social ou de um acordo utilitário.
Se a moralidade e os direitos naturais não forem fundamentados em um Logos criador e legislador, o que acontece é que o conceito de direito natural degenera para algo mais frágil, como um simples acordo utilitário. Nesse cenário, os direitos do indivíduo se tornam algo acordado entre os membros de uma sociedade, em vez de princípios imutáveis e universais. Os direitos podem ser negociados, alterados ou ignorados conforme o interesse do momento.
IV. Fundamento científico: a racionalidade moderna é filha da fé cristã
A ciência moderna só foi possível no contexto cultural cristão. Nenhuma outra civilização — nem a grega, nem a islâmica, nem a chinesa — produziu o método científico como o Ocidente cristão o fez.
Isso se deve a quatro premissas teológicas:
-
Criação racional: O mundo é ordenado por um Deus racional.
-
Distinção entre Criador e criatura: A natureza não é divina e pode ser estudada sem sacrilégio.
-
Valor do trabalho e da observação empírica, herdado do monaquismo.
-
Autonomia institucional, presente nas universidades medievais.
A doutrina cristã da Criação ex nihilo ensina que o mundo foi criado por um Deus racional, sábio e pessoal. Portanto, o cosmos é ordenado, possui leis, e pode ser compreendido pela razão humana — que é imagem do Criador. Isso contrasta fortemente com as cosmovisões panteístas ou mitológicas, onde o mundo é cíclico, arbitrário ou habitado por forças caprichosas.
Sem essa fé no Logos criador, não há razão para crer que a natureza tenha uma ordem inteligível universal e constante, que pode ser descoberta por observação e dedução. A ciência moderna só é possível porque, antes de investigar a natureza, pressupôs-se que ela era investigável — e isso foi uma herança direta do pensamento cristão.
Homens como Bacon, Newton, Kepler e Galileu viam na ciência um modo de glorificar o Criador. O ateísmo cientificista é, portanto, parasitário da teologia cristã, pois toma seus frutos e rejeita suas raízes. A ciência moderna nasceu como filha legítima da fé cristã. E os que hoje a usam contra sua mãe, ou são ingratos, ou ignorantes.
V. O cristianismo como barreira à revolução cultural
O cristianismo é a barreira mais sólida contra a infiltração revolucionária. A chamada "marcha gramsciana", que visa corroer os fundamentos morais da sociedade para subjugar o indivíduo ao coletivo, encontra sua resistência mais firme nos princípios cristãos. A fé cristã, ao proclamar a existência de uma verdade objetiva, de uma lei moral imutável e de uma dignidade humana que transcende o Estado e o consenso social, imuniza a civilização contra o relativismo e o igualitarismo nivelador do marxismo cultural.
Além disso, o cristianismo é uma tradição milenar, profundamente enraizada no cotidiano das pessoas, não sendo uma novidade a ser imposta ou implementada, mas uma força presente há séculos, que permeia a estrutura social, moral e cultural da sociedade. Sua presença constante nas comunidades, desde os tempos mais antigos, oferece uma resistência robusta contra qualquer tentativa de subverter a ordem natural e moral estabelecida.
Não por acaso, tanto Karl Marx quanto Antonio Gramsci identificaram no cristianismo o principal obstáculo à realização de seus projetos revolucionários. Marx chamou a religião de "ópio do povo" porque sabia que uma alma ancorada em Deus não se submete facilmente ao poder terreno; Gramsci, mais sutil, propôs a destruição da cultura cristã como pré-condição para o triunfo do socialismo. Sem essa âncora transcendente, a sociedade torna-se presa fácil das engenharias sociais que pretendem redefinir arbitrariamente o homem, a família e a liberdade.
Conclusão
O libertário anticristão, consciente ou não, nega as fundações mesmas do edifício que habita. Ao rejeitar o cristianismo, cava o abismo sob os próprios pés, privando o ideal libertário de sua base moral, cultural e racional. Ele defende a ética voluntária, a liberdade individual e a ordem espontânea, mas sem o solo metafísico e histórico que torna esses princípios inteligíveis e possíveis. É um erro tentar preservar a liberdade em termos absolutos sem reconhecer as raízes cristãs que a sustentam, pois o cristianismo é a única tradição que a legitima e a viabiliza.
Negar o cristianismo é racionalmente insustentável. A liberdade, como a conhecemos, é filha da fé cristã, que oferece a base moral e metafísica que torna a liberdade tanto desejável quanto possível. Mesmo que ateu, o libertário que ama a liberdade deveria, no mínimo, respeitar — e, idealmente, redescobrir — essas raízes cristãs. Pois sem fé, restam apenas o niilismo e o relativismo, que, eventualmente, desaguam na servidão.
Como nos ensina a tradição: Ubi fides ibi libertas — onde há fé, há liberdade.
-
-
 @ d360efec:14907b5f
2025-05-12 04:01:23
@ d360efec:14907b5f
2025-05-12 04:01:23 -
 @ 09d5c0a0:2ebbe260
2025-05-12 17:08:20
@ 09d5c0a0:2ebbe260
2025-05-12 17:08:20*For some people, Bitcoin is about saving for retirement. For others, it’s about eating tomorrow. __I first shared the idea of a “Bitcoin Privilege Curve” at the Plan B Forum 2025 in El Salvador. And it still guides how I see Bitcoin today—especially here in Uganda. __Bitcoin shows up differently depending on where you are in life. What it gives you depends on what you need most. __In Uganda, Bitcoin shows up as survival and uphill battle towards financial empowerment to the largely financially illiterate community. __Sometimes it’s food. Sometimes it’s school fees. Or even a skill. We receive Bitcoin donations that allow us to feed orphans, support teachers, and build small projects that teach these children how to farm, save, and think differently about money, __They’re learning how to live better. A child who knows how to grow food and save in sats is building wealth from the ground up. That’s what the lower end of the curve looks like: *Cheap transactions: Many of the people we work with don’t have bank accounts and the cost of accessing, setting up and maintaining a bank account is just unnecessary. Bitcoin lets them send and receive money within themselves almost at no fees, a better option than the exploitative fee structure by mobile money service providers and most banks. Cross-border remittances: We’ve seen Bitcoin move across borders in minutes with no forms, no gatekeepers. I can instantly and cheaply pay for a friend's grocery shopping in Kenya by sending Kenyan shillings into a Grocery Vendor's Mpesa straight from my Bitcoin wallet via Tando. Wealth multiplication: Even saving one sat creates a shift. It teaches patience. It grows over time. Bitcoin is a wealth multiplier for most underprivileged or privileged people, we taught Bitcoin and its principles to former students at Makerere University that have now entered the job market, from testimonials Bitcoin is helping them achieve their savings goals faster than their colleagues.
__Now go higher up the curve, and Bitcoin looks different. ****Wealth preservation: For someone with savings, Bitcoin protects that value over time, especially in regions with unstable currencies, the Argentina, Zimbabwe and Venezuala currency devaluation scandals always remind me that, you can do everything right and still end up losing all your hard earned value to mediocre goverment policies. Inflation hedge: Where governments keep printing money, Bitcoin holds its ground. It offers a stable alternative. The fallacy that inflation is a necessary evil no longer holds water, having a currency with a 21 Million coin hard cap enforceable by millions of Bitcoin network participants across the world guarantees no governement intervention. Censorship resistance: No one can freeze, reject or interfere with your Bitcoin and respective transactions. It's easy to assume because its a public ledger, you sacrifice privacy hence transaction integrity but this is far from the case, Bitcoin gives people freedom to transact without interference privately. Choice: Bitcoin doesn’t lock you into one system. You can move in and out of, save, or spend it however you see fit as long as your transactions obey the globally agreed upon, never changing network rules since 2009.
__So no, it’s not fair to compare someone struggling for a meal to someone saving for their retirement. But that’s the point. Bitcoin doesn’t need to be the same thing for everyone.
__With Gorilla Sats , our tourism project, we’re linking both ends of the curve. Bitcoiners from around the world visit our communities and spend their Bitcoin with local vendors. It’s not charity—it’s a circular economy. The people higher up the curve get meaningful experiences. Locals get income, exposure, and proof that their sats are valuable.
__In traditional finance, someone without a Visa machine can’t do business with someone carrying a card. The tourist who can't easily use mobile money and is hesistant because of exchange rates will spend comparably less but with Bitcoin, all you need is a phone even a basic button one because with now Machankura 8333, Bitcoin moves via USSD.
__Bitcoin offers privilege—but not the kind that excludes. It offers access, ownership, and freedom based on where you are in life. So no, it’s not fair to compare someone struggling for a meal with someone protecting their portfolio. But that’s the point.
__And if we build for everyone on the curve, we all move forward.
__If you’re building for Bitcoin adoption, think about the full curve. What’s it solving where you live? And who still needs a way in?
-
 @ eabee230:17fc7576
2025-05-12 14:38:11
@ eabee230:17fc7576
2025-05-12 14:38:11⚖️ຢ່າລືມສິ່ງທີ່ເຄີຍເກີດຂຶ້ນ ຮອດຊ່ວງທີ່ມີການປ່ຽນແປງລະບົບການເງິນຈາກລະບົບເງິນເກົ່າ ສູ່ລະບົບເງິນໃໝ່ມັນເຮັດໃຫ້ຄົນທີ່ລວຍກາຍເປັນຄົນທຸກໄດ້ເລີຍ ນ້ຳພັກນ້ຳແຮງທີ່ສະສົມມາດ້ວຍຄວາມເມື່ອຍແຕ່ບໍ່ສາມາດແລກເປັນເງິນລະບົບໃໝ່ໄດ້ທັງໝົດ ຖືກຈຳກັດຈຳນວນທີ່ກົດໝາຍວາງອອກມາໃຫ້ແລກ ເງິນທີ່ເຫຼືອນັ້ນປຽບຄືດັ່ງເສດເຈ້ຍ ເພາະມັນບໍ່ມີຢູ່ໃສຮັບອີກຕໍ່ໄປເພາະກົດໝາຍຈະນຳໃຊ້ສະກຸນໃໝ່ ປະຫວັດສາດເຮົາມີໃຫ້ເຫັນວ່າ ແລະ ເຄີຍຜ່ານມາແລ້ວຢ່າໃຫ້ຄົນລຸ້ນເຮົາຊຳ້ຮອຍເກົ່າ.
🕰️ຄົນທີ່ມີຄວາມຮູ້ ຫຼື ໃກ້ຊິດກັບແຫຼ່ງຂໍ້ມູນຂ່າວສານກໍຈະປ່ຽນເງິນທີ່ມີຢູ່ເປັນສິນສັບບໍ່ວ່າຈະເປັນທີ່ດິນ ແລະ ທອງຄຳທີ່ສາມາດຮັກສາມູນລະຄ່າໄດ້ເຮັດໃຫ້ເຂົາຍັງຮັກສາຄວາມມັ້ງຄັ້ງໃນລະບົບໃໝ່ໄດ້.
🕰️ໃຜທີ່ຕ້ອງການຈະຍ້າຍປະເທດກໍ່ຈະໃຊ້ສິ່ງທີ່ເປັນຊື່ກາງໃນການແລກປ່ຽນເປັນທີ່ຍ້ອມຮັບຫຼາຍນັ້ນກໍຄືທອງຄຳ ປ່ຽນຈາກເງິນລະບົບເກົ່າເປັນທອງຄຳເພື່ອທີ່ສາມາດປ່ຽນທອງຄຳເປັນສະກຸນເງິນທ້ອງຖິ່ນຢູ່ປະເທດປາຍທາງໄດ້.
🕰️ຈາກຜູ້ດີເມື່ອກ່ອນກາຍເປັນຄົນທຳມະດາຍ້ອນສັບສິນທີ່ມີ ບໍ່ສາມາດສົ່ງຕໍ່ສູ່ລູກຫຼານໄດ້. ການເກັບອອມເປັນສິ່ງທີ່ດີ ແຕ່ຖ້າໃຫ້ດີຕ້ອງເກັບອອມໃຫ້ຖືກບ່ອນ ຄົນທີ່ຮູ້ທັນປ່ຽນເງິນທີ່ມີຈາກລະບົບເກົ່າໄປສູ່ທອງຄຳ ເພາະທອງຄຳມັນເປັນສາກົນ.
ໃຜທີ່ເຂົ້າໃຈ ແລະ ມອງການໄກກວ່າກໍ່ສາມາດຮັກສາສິນສັບສູ່ລູກຫຼານໄດ້ ເກັບເຈ້ຍໃນປະລິມານທີ່ພໍໃຊ້ຈ່າຍ ປ່ຽນເຈ້ຍໃຫ້ເປັນສິ່ງທີ່ຮັກສາມູນລະຄ່າໄດ້ແທ້ຈິງ.🕰️ເຮົາໂຊກດີທີ່ເຄີຍມີບົດຮຽນມາແລ້ວ ເກີດຂຶ້ນຈິງໃນປະເທດເຮົາບໍ່ໄດ້ຢາກໃຫ້ທັງໝົດແຕ່ຢາກໃຫ້ສຶກສາ ແລະ ຕັ້ງຄຳຖາມວ່າທີ່ຜ່ານມາມັນເປັນແບບນີ້ແທ້ບໍ່ ເງິນທີ່ລັດຄວາມຄຸມ ເງິນປະລິມານບໍ່ຈຳກັດ ການໃຊ້ກົດໝາຍແບບບັງຄັບ. ຖ້າຄອບຄົວຫຼືຄົນໃກ້ໂຕທີ່ຍູ່ໃນຊ່ວງເຫດການນັ້ນແຕ່ຕັດສິນໃຈຜິດພາດທີ່ບໍ່ປ່ຽນເຈ້ຍເປັນສິນສັບ. ນີ້ແມ່ນໂອກາດທີ່ຈະແກ້ໄຂຂໍ້ຜິດພາດນັ້ນໂດຍຫັນມາສຶກສາເງິນແທ້ຈິງແລ້ວແມ່ນຍັງກັນແທ້ ເວລາມີຄ່າສຶກສາບິດຄອຍ.

fiatcurrency #bitcoin #gold #history #paymentsolutions #laokip #laostr
-
 @ d360efec:14907b5f
2025-05-12 01:34:24
@ d360efec:14907b5f
2025-05-12 01:34:24สวัสดีค่ะเพื่อนๆ นักเทรดที่น่ารักทุกคน! 💕 Lina Engword กลับมาพร้อมกับการวิเคราะห์ BTCUSDT.P แบบเจาะลึกเพื่อเตรียมพร้อมสำหรับเทรดวันนี้ค่ะ! 🚀
วันนี้ 12 พฤษภาคม 2568 เวลา 08.15น. ราคา BTCUSDT.P อยู่ที่ 104,642.8 USDT ค่ะ โดยมี Previous Weekly High (PWH) อยู่ที่ 104,967.8 Previous Weekly Low (PWL) ที่ 93,338 ค่ะ
✨ ภาพรวมตลาดวันนี้ ✨
จากการวิเคราะห์ด้วยเครื่องมือคู่ใจของเรา ทั้ง SMC/ICT (Demand/Supply Zone, Order Block, Liquidity), EMA 50/200, Trend Strength, Money Flow, Chart/Price Pattern, Premium/Discount Zone, Trend line, Fibonacci, Elliott Wave และ Dow Theory ใน Timeframe ตั้งแต่ 15m ไปจนถึง Week! 📊 เราพบว่าภาพใหญ่ของ BTCUSDT.P ยังคงอยู่ในแนวโน้มขาขึ้นที่แข็งแกร่งมากๆ ค่ะ 👍 โดยเฉพาะใน Timeframe Day และ Week ที่สัญญาณทุกอย่างสนับสนุนทิศทางขาขึ้นอย่างชัดเจน Money Flow ยังไหลเข้าอย่างต่อเนื่อง และเราเห็นโครงสร้างตลาดแบบ Dow Theory ที่ยก High ยก Low ขึ้นไปเรื่อยๆ ค่ะ
อย่างไรก็ตาม... ใน Timeframe สั้นๆ อย่าง 15m และ 1H เริ่มเห็นสัญญาณของการชะลอตัวและการพักฐานบ้างแล้วค่ะ 📉 อาจมีการสร้าง Buyside และ Sellside Liquidity รอให้ราคาไปกวาดก่อนที่จะเลือกทางใดทางหนึ่ง ซึ่งเป็นเรื่องปกติของการเดินทางของ Smart Money ค่ะ
⚡ เปรียบเทียบแนวโน้มแต่ละ Timeframe ⚡
🪙 แนวโน้มตรงกัน Timeframe 4H, Day, Week ส่วนใหญ่ชี้ไปทาง "ขาขึ้น" ค่ะ ทุกเครื่องมือสนับสนุนแนวโน้มนี้อย่างแข็งแกร่ง 💪 เป้าหมายต่อไปคือการไปทดสอบ PWH และ High เดิม เพื่อสร้าง All-Time High ใหม่ค่ะ! 🪙 แนวโน้มต่างกัน Timeframe 15m, 1H ยังค่อนข้าง "Sideways" หรือ "Sideways Down เล็กน้อย" ค่ะ มีการบีบตัวของราคาและอาจมีการพักฐานสั้นๆ ซึ่งเป็นโอกาสในการหาจังหวะเข้า Long ที่ราคาดีขึ้นค่ะ
💡 วิธีคิดแบบ Market Slayer 💡
เมื่อแนวโน้มใหญ่เป็นขาขึ้นที่แข็งแกร่ง เราจะเน้นหาจังหวะเข้า Long เป็นหลักค่ะ การย่อตัวลงมาในระยะสั้นคือโอกาสของเราในการเก็บของ! 🛍️ เราจะใช้หลักการ SMC/ICT หาโซน Demand หรือ Order Block ที่ Smart Money อาจจะเข้ามาดันราคาขึ้น และรอสัญญาณ Price Action ยืนยันการกลับตัวค่ะ
สรุปแนวโน้มวันนี้:
🪙 ระยะสั้น: Sideways to Sideways Down (โอกาส 55%) ↔️↘️ 🪙 ระยะกลาง: ขาขึ้น (โอกาส 70%) ↗️ 🪙 ระยะยาว: ขาขึ้น (โอกาส 85%) 🚀 🪙 วันนี้: มีโอกาสย่อตัวเล็กน้อยก่อนจะมีแรงซื้อกลับเข้ามาเพื่อไปทดสอบ PWH (โอกาส Sideways Down เล็กน้อย สลับกับ Sideways Up: 60%) 🎢
🗓️ Daily Trade Setup ประจำวันนี้ 🗓️
นี่คือตัวอย่าง Setup ที่ Lina เตรียมไว้ให้พิจารณาค่ะ (เน้นย้ำว่าเป็นเพียงแนวทาง ไม่ใช่คำแนะนำลงทุนนะคะ)
1️⃣ ตัวอย่างที่ 1: รอรับที่โซน Demand (ปลอดภัย, รอยืนยัน)
🪙 Enter: รอราคาย่อตัวลงมาในโซน Demand Zone หรือ Bullish Order Block ที่น่าสนใจใน TF 1H/4H (ดูจากกราฟประกอบนะคะ) และเกิดสัญญาณ Bullish Price Action ที่ชัดเจน เช่น แท่งเทียนกลืนกิน (Engulfing) หรือ Hammer 🪙 TP: บริเวณ PWH 104,967.8 หรือ Buyside Liquidity ถัดไป 🎯 🪙 SL: ใต้ Low ที่เกิดก่อนสัญญาณกลับตัวเล็กน้อย หรือใต้ Demand Zone ที่เข้า 🛡️ 🪙 RRR: ประมาณ 1:2.5 ขึ้นไป ✨ 🪙 อธิบาย: Setup นี้เราจะใจเย็นๆ รอให้ราคาลงมาในโซนที่มีโอกาสเจอแรงซื้อเยอะๆ ตามหลัก SMC/ICT แล้วค่อยเข้า เพื่อให้ได้ราคาที่ดีและความเสี่ยงต่ำค่ะ ต้องรอสัญญาณ Price Action ยืนยันก่อนนะคะ ✍️
2️⃣ ตัวอย่างที่ 2: Follow Breakout (สายบู๊, รับความเสี่ยงได้)
🪙 Enter: เข้า Long ทันทีเมื่อราคาสามารถ Breakout เหนือ High ล่าสุดใน TF 15m หรือ 1H พร้อม Volume ที่เพิ่มขึ้นอย่างมีนัยสำคัญ 🔥 🪙 TP: บริเวณ PWH 104,967.8 หรือ Buyside Liquidity ถัดไป 🚀 🪙 SL: ใต้ High ก่อนหน้าที่ถูก Breakout เล็กน้อย 🚧 🪙 RRR: ประมาณ 1:3 ขึ้นไป ✨ 🪙 อธิบาย: Setup นี้เหมาะกับคนที่อยากเข้าไวเมื่อเห็นโมเมนตัมแรงๆ ค่ะ เราจะเข้าเมื่อราคา Breakout แนวต้านระยะสั้นพร้อม Volume เป็นสัญญาณว่าแรงซื้อกำลังมาค่ะ เข้าได้เลยด้วยการตั้ง Limit Order หรือ Market Order เมื่อเห็นการ Breakout ที่ชัดเจนค่ะ 💨
3️⃣ ตัวอย่างที่ 3: พิจารณา Short สั้นๆ ในโซน Premium (สวนเทรนด์หลัก, ความเสี่ยงสูง)
🪙 Enter: หากราคาขึ้นไปในโซน Premium ใน TF 15m หรือ 1H และเกิดสัญญาณ Bearish Price Action ที่ชัดเจน เช่น แท่งเทียน Shooting Star หรือ Bearish Engulfing บริเวณ Supply Zone หรือ Bearish Order Block 🐻 🪙 TP: พิจารณาแนวรับถัดไป หรือ Sellside Liquidity ใน TF เดียวกัน 🎯 🪙 SL: เหนือ High ของสัญญาณ Bearish Price Action เล็กน้อย 💀 🪙 RRR: ประมาณ 1:1.5 ขึ้นไป (เน้นย้ำว่าเป็นการเทรดสวนเทรนด์หลัก ควรใช้ RRR ต่ำและบริหารขนาด Lot อย่างเข้มงวด!) 🪙 อธิบาย: Setup นี้สำหรับคนที่เห็นโอกาสในการทำกำไรจากการย่อตัวระยะสั้นค่ะ เราจะเข้า Short เมื่อเห็นสัญญาณว่าราคาอาจจะมีการพักฐานในโซนที่ถือว่า "แพง" ในกรอบสั้นๆ ค่ะ ต้องตั้ง Stop Loss ใกล้มากๆ และจับตาดูใกล้ชิดนะคะ 🚨
⚠️ Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัวของ Lina เท่านั้น ไม่ถือเป็นคำแนะนำในการลงทุนนะคะ การลงทุนมีความเสี่ยง ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบค่ะ 🙏
ขอให้ทุกท่านโชคดีกับการเทรดในวันนี้ค่ะ! มีคำถามอะไรเพิ่มเติม ถามมาได้เลยนะคะ ยินดีเสมอค่ะ! 😊
Bitcoin #BTCUSDT #Crypto #Trading #TechnicalAnalysis #SMC #ICT #MarketSlayer #TradeSetup #คริปโต #เทรดคริปโต #วิเคราะห์กราฟ #LinaEngword 😉



-
 @ 4bc7982c:4cb5c39d
2025-05-12 14:21:38
@ 4bc7982c:4cb5c39d
2025-05-12 14:21:38-----BEGIN PGP PUBLIC KEY BLOCK----- mQINBFav2jMBEADPCRsFp9Vtw0vlkeho2v8lIPblVNNeW43HLNXeEGvgn+gaK5sW 9H5mbp6ZLEjbdEr7zc3eu7iLFudw9IdJCLKYcqkXWBpAQF7JF6l4J18oOQK1Tfzc QyU5jWuAcc+Ds8REW91X/N9Ae/QF+dtRyuv1ILFKZ88G2za/TdV06PuNdyi3qTlD 5HPVhd5YrZyY7GVG1gTi7Wtj6tONGjjQARR6T1LDuN75QmoDvw3m68U5QnoECGg4 BFAdPrnFxYpTCl6SyV9AsCfzTwP2mIkLKZi7X/wSubt4b+nhPMuFeZ/6XFCfHCD4 mEcQudyXByi7FgAXmX+UPS1iFtaXG8UJHM4Fq2k5FcjdLXW2s0kKk915XVEE9Q4Y wWQpTonr9FwgT+aSbV7UX8ihNhNCSQAv1RnIIt8t9hncztfZD7g/FMj4FfZ8GkI0 gmn3DliSlswBZbr1rN0HTitAzYKNUsiinIxwICfj9yRTcQ92F0ML+zwQB5UOXjEJ ra+D3tGjyVCNKO940rbjvj/QAvakoNBdCnbaZDKf26Hc0qpcn3DvGei0QLFJ2gmz EnK1dW4kftcJE8piibvq35EEptqkDiCMlI0Eq819vtJBumF3ZSBjMeEB1IPfSvDG 1OoUXXS0TGwCGstjMTRQ1S2D8fDb0ENBrbdhyWXZVQFzxi/YMwkNGswDoQARAQAB tBpzaGlub2hhaSA8YnRjaW5mb0BzZGYub3JnPokCNwQTAQgAIQIbAwIeAQIXgAUC Y+g7QQYLCQgHAwIGFQgCCQoLAxYCAQAKCRBKdYg8wbHTTG6OD/wJ9V3tjvaerA6Y GViWU6h0Nrvjs6/NWq48K3hP9eqy9n7CKVOviCjglF/yf1FEfEDg7LKYtFYLs1pf MFzNolynfGearK7HQeOXRoNFfkDqQWcjPWeVWhkEgxrqq9AMg+7gHMMtKnHWezJT E4NaAui7uW7rTiOvS8PT8+Y3uATermzJ0Cmb1c0su/s9in3bPwnmxJpbj9EruOWg MVY8Hov5fEJTwghIwoVBR2D4nWObQMWQsiNrEG/XdPeE1XzHGLrSmH64o6T2vWK2 XkQU6TVDBKhsIy0EjX9B36Hx+MmFx1pfHfxtGpAgZKwnEnMIoNc2vvrkjJhnRCUQ 1MfMoPDnn01mOT/kNkijyTUlh4rYeqa/A5JuqLbQ6qWz4e9rodu9C6/drn7Ivk/D ipRyMihNKbWq1PkAr7I9YQ/1NAM8ZmUE/bFL7/t6rDsa5IinwUeu/WGqNmKHIo0o u5vQD9zwmYOqeZLo2vzmmr/NkaRD7/3j5pb81MTjZzqTh/BGI31TEbjWpJ4StJ4g 2QNcXamGa/7/TpgI5u2EQojdvUojzSg7V3/ZNsNaJnDnqtZNzY7n2q4qvE2H/xJq z5y0SsTgpMPktt+ljg/T3po/LGQIcCPE4EBpSBKSpi0VWvkGVM2sraUCzP82c/X+ ztr12YwcckdET9SWDtSloE942tXKO4kCOQQTAQgAIwUCVq/aMwIbAwcLCQgHAwIB BhUIAgkKCwQWAgMBAh4BAheAAAoJEEp1iDzBsdNMrLMP/1pQZUXNzG9FlhBBGA8X ko+ObEvuVUvtZzTu8DXrQGDp/DYQq+O7YWhZ8WwyxYJx718bkIemHP5IbXbzmeS3 Nijf1mszrCbmw7QZ496YTihoZxyeb8MHYECPAiUbz9Ie2S6/isF45LZX3SbkwlYc M5UfV4iaXqvKSuydRJ8Xk68rn+AiEXFrv1vcGy7cqDz4PBOd9ZJwiAWhr0m9hMZT uDqYPI8choUh3uhpMIEf9YLD77ru1xl0Uba8e34qrOs+Secfv81ItbFION9z0A17 W2/q01dQfojpcoC+YS3CXXCJGm5TwYniIWVUmtL4eIfg6T/ZX5o5Am3aj4pQxr+E y/NNkUvplXZ+nG3fG4mthY4r+NV4E/RSsZJDU55BAWhZj3fHVhu7Q40yVMHLJNP9 KKCdacd/WWJtUX3Z1X/mQplJcMCYwhvdPNCctDpHrEyuIlvDvJuqbCY5eBa0hk8z jRNA9IghWW7JMzcnQR5u6FXWiqmcfFOEJwDUu8hM057Q6e6/FRPjlmua6SzcMK+k ERS+AwAIX4BIaLCnE7ndizQ/y6ek2hpKFXzPBLmxLyID91/wlA6NzbtyZkgZvJ7X g/7Rtt4FyZwKZqbfBFrjzLIyFTkmJ0lSPCSuWna5vaSg1HXPfc05wOUXsGV8xA8D zrolAoj4OIo//H2YMvLy5Giz0f8AACeO/wAAJ4kBEAABAQAAAAAAAAAAAAAAAP/Y /+AAEEpGSUYAAQEAAAAAAAAA/9sAQwAIBgYHBgUIBwcHCQkICgwUDQwLCwwZEhMP FB0aHx4dGhwcICQuJyAiLCMcHCg3KSwwMTQ0NB8nOT04MjwuMzQy/9sAQwEJCQkM CwwYDQ0YMiEcITIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIy MjIyMjIyMjIyMjIy/8AAEQgAyADIAwEiAAIRAQMRAf/EABwAAAIDAQEBAQAAAAAA AAAAAAYHAAQFAwIIAf/EAEkQAAEDAwIDBAcFAwgIBwAAAAECAwQABREGEgchMRNB kaEUIjJRcYGxFSNCYcEIUtEWFyQlM1OSohg0YmNzgpPSQ1RVcpTC4f/EABkBAAMB AQEAAAAAAAAAAAAAAAABAgMEBf/EACIRAAICAgIDAQEBAQAAAAAAAAABAhEDEiFB EzFRBCJhgf/aAAwDAQACEQMRAD8AAbvwd1NZkuKf9GWhH4miog/5aEpOn50UkLQC R7s/rX0K1xpmuEJk6RW4g9exloX5GuMvibpeY2U3TRFxCVclH0dKh4irpfBWfOog P4yUgVyMdwHG2n8q8cGZQw/CfiLV3dk4nH58q/E2Pg/NwpjUaWCT0W4QfMUUgEN6 C9tzgAfnX43DdcHq4p/p4XaLnpzA1iypJ6BTqD+teU8CkryYd/jOJ7iBn6UUg5EM LbII9kVbg6emTpAZSppsnvcJApxyOBd/59nNiLx05kVjyeEesYSj2cL0gD+6dHOi ogZ8DgVqO4xw8zcbVgjOC8rPkmhu8cO7zZXFokKZVsOCUbv1FFyLBru0glqLdI5/ 2Mn6VbTf+IEMhMiRJUnG3ZIjBWfmRRURWxPrirQspJTkcq/RDdV0xTYe1Jc3QW7h YLPKHeVxSlXiDWQ87ZXlZd0p2ZByr0WUpvPjmqSiDbMDTWg7nqdakxZENnb3vubc +Ao1T+zvqpYym4Wkj3h1f/bWIpzTvLbbb3BXn2mZKXCPHFbdvviIiQImr79EGOQe ZCgPjg0nFdMSk+z9/wBHXVf/AKhaf+ov/tqf6Ouq/wDz9p/6q/8Atrft2v782/ln XMGU2kY7OdAUgH/mAzW9B4lanW+cq01NQPwNSy2o+NTqyrFPO4Oaht7qm3JEFRBx lKl8/wDLVNPC29KyPSYQI961fwp9t6/vTqgqToztmu9Uae04fkDiuL2tbSFf0/Q1 8ZCj6znogUB80mjVlKhDq4ZXhPWTC/xq/hVJ/Qs+ODvlw+XuUr+FPh3UfDt93Y8u 4QlH+9YWgDxFeC3w5lqAZ1THCjyw4sfrRqPg+endOyWjjtmD+YJ/hXH7Ekf3jXia +j/5C6amDETUNvcUroN6D+tVX+D6lt5iy4iyf3TVJR7Jkn0Ii26Rm3KSlhuRFbUr oXVkD6Uao4CamcY7VE+1KTt3eq8o/wD1oqk8HryzktJS57tjnOqY0jra0J+4Vcmw ByKCVAU6gZtyFvdNAXa0qUl9xhRT12bv1FSmC7c9dQhskPreQOqZEYHPzxUqtYBc hTtKlME7FOIPfg4q43ebnGQezlvpJ9yzX0C3qrhFfiS8iEy4eoejls/TFezw/wCG moGyqDMaST0LEkcvkaj0aUINrUl1BClvhwjudbSr9KujUvapPptmtkjPXDZQfKnH J4B2p5sGDeHkH3qbCgfCh2ZwEvUcqMSdGkp7gfUNPZCoXyZumHkff2F1pZ6lh7p8 M1aaNkSE+gX26wFk9FlRCfA1rT+Eeq4gUr7OLgH90QrND0jSN9hubH7dJQT72zTt DQSQp2qY53WniAh0p9lt50pz/izW7D1lxVgrKu1hXJHuOwj5EEUrXYLrR2rScjuK ajfpjQ+7cWgZ/CsilaHSHQ1xo1Tb1BF20gVH8RacI/Q1qxOPWnpDgbn2qbG7iVIC wKSsW/32IrLdwlJ/LfkedXV6wmrAEuJCkj8RcjgE/MU6iNJD0b4gcNLsrD0uElau X37JSfpV1myaBvCCYbkFee9h8Z+tfPxv9ikIKZOnGUk/iYcKT51G2NHvthYfuNue V1ASFpHzHOp1XQOI/JHCyyyMqjvLQD05BQrIkcH0bVFmSws9yVNkedLCEJUcZsev XAB7KHXFtjwPKiOFqbiVCSFsTY9zR0GVIXn4YOaWrJ1NWRwkmZ5R2T+bazWa7w3m RchcV/HvCc1bb4u6yty9l20yhZ7i2FDNacXj/ZgsN3O0Toa+8gpWKlwbGkD8TSzl tkJc7HtOfNDoIzTLtsOxPxWk9q/EexzDT6gM/PlVeJxU0NdkpC57aNwyBIaKa2oz +lryN8OVDd/4TgBHyqanH0Pj4fjmnS+3hi7OLQR7LzaHUnyofuOhj2brztrs8wJS TybUyo+HKi9uysJAUw+4kdxCs1+O2l9aFIEtSkqGCFE01kl2SJF3T+m5MdyQ7ZJ8 FaTgvRF9okfOqH2NBSlRt+sZcRwD1Q+laPMGm1O0YVRlMI7TslHJS2vA8KE7joV3 CkbnkoHetGRTWV9oaBuIeIkUA2nV7E9tPQGQlXyIUK2GNc8U7V61wsUe4N95bTt8 01hSNBPtKKmZSASe7Kaz1QdVWlRMSfJCEnklt448KayRfspJBwzxtW24W73pKQxj qpCgryIqUEHV2qYQxMaTJSe6QylVSrTgS0gPTcdJSifSbDJYUe+NI5eBqzHiaSc3 GPerhbz/AL9rI8RXiZw91RbiRJsspPLOQncPKsR61SWSQ/FeQR3LQRVbDDCDDuzL gcsevGlbT6qTKUg+BokjX/i3bAC1KbuKCeXrodz4EHFKURdp9nmPfXdrtmFb2XHW le9Cyk+VCkuxUN1rjVre2L23XTbS0jkT2S2/MZFbET9oO2LA+1LFJZ7tyCFjzpOx tU6ggoKGbtKCP3VnePOryddT3AlM6DbZqU9zsYDPzFH8MKHVG4m8NL/lEtpppajj EmKAfEVcTYOGV/GIjsEKHXsXtp86Rwv2mLgpX2npdltSvxRHijFeVQdCSQOyk3SA 4T1JStIH1o0j0w5Ha9wcsEpBXBuDwz09ZKh5VhTOB0oEmNcGFjuCwU0vIlljtrSq x6/bjlPMB9xbWfh3URx5fFC2JSYOoGrkjPIIfQ/kfDrih430w5Okvg9fWNxTDQ8B 0U26Dn5UPv6AuUdakvQZKVJ6jYaLY/FTiFaXdl50+2+kDqhhST5ZFakX9oCGghFz skhgj2lJUD4A1Gkh2K13TTycpSopx1Cga8N2O5x/WjukEc/VUU074nFTh/eloakY aUsZHbsY8xWu0xoK8hJjTIJUegbkBKvDNS4zQWIhi46nt3NMuT+e5W8edXUajub4 2zIcCUOn38VP1FO9egrQ+gmNIWM9MLChVNXDlAJKZDax3BScUtmh2KiDFh3p9UY6 SjOOhO4+iu7CfgDWo7w+s4b3+g3mAo+0EtbgPCj9Oi34D/pEaMjtE9FNq51stXO7 w0BD0RagnvUmluwsVsW0XOAMWjWLzIT7LcgLRjx5VdTduJ8L14syFcmx1wpCvLka ZLt6Yfb2yrelYPUKGfrQLqq12iWtDsCCYbuPWUydufCrU49jtMzEcWNcWtzF2000 tsdVNoWk/qK04vHu1ZCLjZprHvKBvA+VBjzmpbVziXOZs7krVvHga5K1fektlFxt 8Cck/wB9FAPiKr+GHA1YnFLQN3TtXMbbJ6pfZKSK0UM6NvIBjTYpUvmOzeAPgaRr 100pcF/1hpUMrPNTkV4p5/Cqi7doOSCUXS629WeSXWwseI7qXjRLHtK4ew5SMxpq v+YBQ8qlJqJp6S2oL09r5sHqltUlTZ8DyqUtCbCdj9oZ6PtTdNMPN9ylIc2+AUK1 Y/G7Qt0XsuFueY3cip5hKx4ikO1rK+oTtcmJfT7nmkrz413VqqNISBNsNve95bQW yfz5VVREP9M7hFqFeN1p7VfLJHZK/SvbnCnQd1QVQZGzd+KPKChXz8zcNJyEkSLX Lik/iZWFgeNWGY2nspNu1JMiEnmHmSkD5pNUoJ9hY4pvAKK4k+hXhaPd2re6sGZw GvLWfR5cSQPiUnzoZgz9WRQr7J1yxJS2PVT6Xjl8FVuQtfcU7ad7rCbi2ocgW0q+ YKTmh430w2MeZwh1TEWoC2LdA72lBQNY0jRN4hJK5NtktJHUqaVgeVMSNx8vURQR dtLnlyKmypJ8CK34nH/S0lGyfCmxieRCmwsUtZ/B2ItVtWkHLasD8uVeEQnmnAtj e2pPRTZKSPCvpJGtOGt7ZSl2bbcHmEvI2Hn8qso0joS7JPogiKKu9h8Z+tS7XtDs +eoeotR2zIj3GWkHkQpRUD41oDXt6cQlubHgzUp7noqefzxTlf4PWlxRVHnPoSeg UAqsqRwceTvMeYw4PwhSSCaFOgFZ9uaemhRuekY6VE+1CcU0fCvwsaCmJTtTc7Y5 nmtWHQKNZPCq8MZxCS4P92rNZEnh9OY5vW19H57CRV+ZhwVYdtZbVm0a+Q2ceql4 qbJPjiiCHP4lWxKfRLzFuSP3Q6lz686FpGkFt81JUkjplJFWYukpTyUGA3K7Ue0p vOKXkT9lew1Y4ka7tqwLppzt0e9tsjPzHKtqDxqtDig1cbdMhu9FDbuANZ1u0Lq1 phsxL9KYUQCUvHcBRBbtGX5RP21cLdNST+KICfGmnjftCo0mtf6QnJAXcY6c9zo2 1aSNLXU7mpUNwn9x4fxqo7w103Kyp+A1vPXsxtHhWLK4MWN1RVGmTIx7tqs4qWsX ViCd3SNteR90tQ9xBzWZI0Il1JAdaUO4KRQ0vhVqKEsm06vkIA6Bzdy86prj8WbE 6sNSftJpA9pSUqCvh31Gi6YFqdw4J3g24LH7yKD7loJqOSDHfZwe8GiBfFTWlpWB c9Ndoke1htSD+oq/E47WZ4bLnZZsdXfyCxT1kArZelQ2vDCxu6jNSnOzxA4bXgf0 iTEZcUMESWigj51Kf9fA4AJ7gVCmK32jU0V5s+yFYyfCsSfwM1VEBMZliUO7Y6Af OqMXQCXiF2HW0FZz6oLqmlA+NaybDxaszZVCurkloDOWZiXPI1pp8JBGbw31VA5S bLJSfcgBf0rEesU6J6r8V9o+5bZFM1HEfipp9vNwt632/Zy/EKh4pruzx8lEhq+a XhvD8W0FJ8FA1Li0AozDdTzwg/GvbD9wiEKjyH2SnoW3VDHnTqHFDhld0g3PTTjL g/cjpI/ymu7cXg7enMR7kYi1dEbijHiKLYCki6t1DDX6lzecHudAWPOrR1rLcA9M tdtk+/cyEk/MU1jwf09PQpdo1Aw+SeilJOPCsuZwLvCSTGfiPo6jCsGhTaFQvkXb Tcn/AFrTamCfxRX+/wCBro1H0knK412usJ0nkCjIH+GiCXwm1JEb3/Zi3Eg4+7IN DcnSc6M4UPRJDax+Etqp+VhRuxHLzHATZeIJIRzCHZC2/lhWaJ4+suKEBKCpUKeg DokoXn5g5pWOWN9Jxg/AivKLbLjqy2txtQORtUU0t0/aDkcrfGjU1vQn7W0oTk81 NbkjzogsnGu1XWSmNItc2K6r99ORSLF61JCRsRcpe33FW4edEFplajvcRSloZcKe RcUhKFeNZ5JRSui0mfRd5b9KtHbQ4jL7hAUlK09RVfS90RPhlBiojPNnattIxg0v NE64lRZP2TdXANpwhSj5UWq/qzVLclC8Rpg7jy3V5j/X/R2Q/PcWn/wORUrw2oKT kHOa913xdqziJUqVKoCVKlSgDMvVukXCIUxZRjvgeqcApP5EUir/AHq522a/Eudp tkotqKSpTACj8xX0RQXqnQqL7LMxhxpt0jCkrTyJ99VGTQ0rEM5e9LSjtn6YW2rv VGexj88GpR1cOEd3JUppuM7+SV4NStlkJ1PnssOIJ949xq5Eud2g84s2S1/7XCKf Kb7wYvwHbxWobqh1U2ps/MjlXQcPeGt7VttOoGmlEZShEhKvrzqbChRwuJGtICQl q8vlA/C4kKB8a22uMN3eTtulotNwHQl1gA0aucBC8lS4N/YdT3ZRnzFDdy4H6pjl QYZjyQOikOYz8jSjIXJnfy40TPUBc9EMIOea4ju3Fd1ROEl1JLU262tXuV66fOsG bw31PABVItMkJHUpbJFYrlkmxiQ8y4z/AMRBTWmwWHTHDuxy2+1sOuooKj6iZH3a j51oxdD8TLatK7Rf25aUjKTGnhXkaVqoKx1KVfCvcd+fb1bosmQwR/duFNG4WNlO quMVh3plQpEhKTzU7EDg8U1ficd7sw52V504hIHIq9ZB8CKW8LiFrCApJavcshPR KyFDzrdY4x34p2XOHAuCfc8wmio9oLDxHF3QV1SEXWyONKzzPYpXj5irTM7hRfHE lqUIzh7juR9eVAC9f6MuaNt30MzvPVyIsI8K5B7hTczhDV5tThHUq3p86lRiykM2 Rw70tMjOyLfe0hKU7v7VKkj40obxIVbZyo0aSF4OAWz1q1cNO6ft9tcmWTVqZueS o+wpX88cqG4gV6YHCd2D31z5Uki4vkNrboLUF9hpmRpLaHMggOKwaMYydQW+xrg3 iMrtGPXYfHMZFEOh7g09bmUpGCU0fpbafa2rSlQ9xFeeoQzcPg7vP4kuAQ0fq9u7 wQh1QS+3yWk8jmjJl5LqeRrMOmLR6QX0RENunqpHKtJmKhgYRnArqxRnBU/RzZp4 p8xVM71KlStznJXCUh9xgpjuJbWfxEZxXepSasCi08phxEd0qWsjO/HWulwVITb3 1RNvpAQS3u6ZqzgZ6VWnNregvtNr2LUggK91SkoIq7Yo5nEvWlrcWJGn23kIOCpK Fc/CpS4vVzv0O4SG2rjIRsWQNquXWpWycaLaSfop/bXDe4rPpWnLhbt34or+8J/P BrsjTXDua4fQdZPw1H2BJjHzIrMuHCzVVu/t7TI+KE7h5UPv6euEUqEiM82E9dyC P0rbYxGDC0VfY33mmtbwH8H1ENTS2T8jyrUEzjVY0qSn0uY2nHrhKHx4jnSe7Bxo +qohSe8HBFaMS+3+CoLi3Wc2R02vq/jRsn0A1muNmt7Q2EXjT7bhT7S1tLbz4cq0 4/Hqy3BopvGmOROFBKkuE/IgUtovFfWENnsH5qZaM5xLaDn1rQHFZmY8F3bR9jmH GCoNbDSqFgMVvVHB+9oSJMVqE4T+NktqHzFdTo3hjfDm23xpsjqEvg+RpcN3/hlc 1lM7TMy3qPMuRniQD+QrqNN8Mrg4pcHWEqBuHJqTHyEn409Y/RB5J4GMPtqVbb00 4M8t6MjxBrAncD7+wD2BjSfdsVj61SicPru20XdM68hyVZyhtmYpoq88ZrWjReMd lRvafkzUA8gXkPj60tfjGCEvhxqGCCX7VIAH7qM/SsV7T8mOr76O42fcpGKZo4ta 7tGEXXT5dCT6yzGWnl39OVaUfjjZJaki5WAJKjzPqq8iKThJAhN+hejoVjIJ7q7Q jho7k86ZWu9VaTvFrBs8FtuQTlbgZ2KH5UuYxL4CWk5JPLArmyJ1yXAN9EasRa5H YyFbUjkCTypw2/U0Z4Aodzn86REPRl0lFLiWFEnmAKMrfDm2wpakMrbIA5mvNnHV 3FnfBbKmOFq6trAIUOdWhJSWyoEUCW5x1zaAVEZ76JkJU3EcWonATWmPPJ8MWT88 F6LibiO0wcYq2iShY5GhyG0qSjeFdTWo1GWhIwauGSbIy4ca4RqhQPQ1+1mffJOB muyPSCK6I5P8Od467LRcSDjPOuEl1DbKlOLCEAc1E9K/EsKCtyqwb867IivtFh0R dhC3Ep9YfAd9Ty3yOEE37BeVoPTN4eccYvqO0USojck4J+dSgKdprSL0laWtXOQn 1cyh9kpwfjUrpWPgJWnVnNPFDidYNybpae1Sn2i9EVjxSauxf2gAslu96YYWk9S2 efgoUurfxT1nbUpQ3dluIT3PIC8+NbbPGKdJSRebDaLjnluUyEHFbLV+0YBt/OTw vvKOxuVgXFB5lYjjr8U10TYeEV+UHYd5MRahhLfbbQD+aSKCFas4cXEBM7Rb0VR9 pcV6vQs/Cm6JJYvVztiz+F9veB86NF0Abv8ABG1z/XtN+ZeBHRWD5isGfwKv7IJj iLIA/cXtJ+RrOZ4asuJDundeQVZPqIcdLSvrWkzZOL2n2wm2XRU5nqCxJS8B/io1 f0YMXDhZqa3p3O2d8pJwC2N/0oak6fmRFlMmI+0r3LbIppfzncUrGB9qWMutpICl uRFDPzTyrQa4+srXsu2lTuxhW0jP+YUtJCEiILzSt7RUkjoQcGtC33W/2xQXEukx kg5wl9WPDNO0cROGF6aH2jaFs9/rxwcH4pNdUWPhPfWyqBdGI7ixkDttpT8lUv6X QCxh8V9bQm9i5/pKc8w+gKz+VXlcW3ZrJbu+k7PMUU47QN7VD86PVcGLPNZ322/N ug9FHaoeVYczgde2t3o70aQnPIhW3I+dTswFu1NRc5y0IYSyHPZQjoPyo10ppeZC mpkOsF1gjKeVDdx01O01dyxLZUy8363vGPfW/H4wXexx0xWI8RaW04BW3k+NY5E5 8GsHQ97IWvR0Es9mQMEEVqSYsJ1re8hvA71V88tftCagQrLltgLHuwRV1P7Qjr6Q idp5hxPfscP61gvztL2W8lu/Q4lOQ2l4aU3/AMtS7TOysElxJ5hOBSxh8WND3I4l xZ9ucx1QcpzRaxedOXiyuRI2omtq+eXhhQH51g/zZEzbzRdWddLXhtxBZU764/Oj qM4laMgilM7/ACOsCVPzL4p1XujpzWavjFpW0PKEO3XSSQPVK3AEn5ZqsX58idiy zjMeYSnrgV7HKkAP2iWAMDTrn/yK0Lf+0Lb3SBIs7zIzgntAcV2RtezlodpUAoJ7 zVVNwjLdW0Fex7RPQUHQOKNmucVUlhK9oTnJ91D1413Gt0pLyoy3Ybg3KCe/NTtz SLjjsGuLV5ts67IjwUNZbT67iUj1jUrVXrvhhdUhNwtrjKz1UWenzFSt0pUJmPK4 ATVEqgXaC+nHILBHmKHp3BXVMXeUwG3gnvZczmtiNw01TCy7pvV8aSUc0pZmKST8 skVcFx412HAXFdmoTyJKEugj5Vpr/pkLeXoK+wl7ZNrlNHuy0TWS9YpjCiCFJI7l JINN1HGvWEBWy7aYbXg4JUhaP/ytNnjTpG4rUL5ptTCiMFWxLufAZp6yXQxDGA8k gkjd7wK7xp11gYTFly2ADn7pwp50+0XPg3qDs0lxiI4rkEqC2jn6V1PC7Rd0bWq2 39vnzTtdSoDzqNmApoPFHXUHalN4cdbSMBMhtKwfjW03xiuTxAvNjtE8YwoqY2qP zovlcCpJG6FdmHUnoFNkedDdx4M6kjlSkRUvpT3tKBz8qakBW/llw+uSiq6aJcZW faciO4HhmuiLXwmu5zHvFxtS180pko3JT+XPNDszQV+hnDtpmo/MtEjyrHVZJbZI U2tOOoKcVW7AYbPDeK/td03r23LIVkJcUWz5H9K3Y9q4sWkqMSe3cWRjapD4Wk/A Gk63bJCFHswoK/2eVXI03UFrXui3Gaxg5wh0gZ+FS5X7A29WzNTO3dbt/Zdbkq6h SMDH5UET23CorUORrduV8u10eS7cpjshxIwFOHNVJBS5GOR176zbGgaPKvIJFXHm U5O0g1x7E9MVLYHlt3CvW5imhw90FO1hH9IRI9GYScBRGcigi0afduDiSpJDYPXH Wvqjhrafs3TrXqbAUjAxisZZFeqKUeLEZrrR0/TcoRJEsSGsbkLAxS6eBQo5JJr6 14kaOOpLX20dOZTI5JH4hXzNeLC/EdWgpIUk4IPLFa3RV2uAdCj76/CskGva2nEK IKTW5oywnUGo48ReOyCgpefdUuVK2Qk7GDoO1lOl2nnRgOZAyOoouu8iHZLE1Ldj IfVySltaeShWnJhNx/RbXFKGylshAPTlXjUWiblqK0R/RZDTrzKdqkhWEn4Vhjbl Kzr1UY8i5kar0ZIBVcdIlKj7S4zxHlUqrdeFuqGSr+qH1Ad7RCh5VK9JTdHI/Yvm PtGGvfGffaPeW3Cn6VuQtcaytikmNe5wSnolbm8eBpvN6i4P6jUEPMphOYz67ZbH j0rsOHXD6+c7RqFKFK6JS+lXkedSpfSQChcbNUobDc+PAnI70yGPa8Kufzp6enE/ begrc44eRXHwOXzFEczgPIUlXoV0YfR1G8YPlWBO4H6iYaK2mmnsdzboJPyp7IDw ZXCK8NntoFyta/e2Sa/EaG4f3FzFo14uOo/+HIRg/pQ7P4eX23qUl+3yUKAycIzy +IoedsMhtRJSsE/vJxRsA12uG+tYjXbab1smUhP9mluYRkeOK7tu8bbCFBxDtwTy O4lDoH0NJ9uPOhncw680R0LThT9DWvC1rrC1KBZvU5KQMAKc3fWmqAaX88GtLaQL rpVBQOSlFK0HPmKtM8YtMXBRRddMraCvaUUJVzoFicadXsYTIciS2x1S+wDn5itV njBap7iUXnRlvfCuSlM4B86VR+AHUa9cLbutLhSzGdP4VIUjHhyrsrhvpC+b3bfd FErORsdCgPlQEq+8JLmkofs1ygKUea2ugPyPSvEqw8Pm4SpNq1rcoihzCOavIAEU qXQBVN4FbwDGuqSf943j6UudXaPf006uHIUhSwMhSDyIri1rrUFhfP2XqeTJabOE CQNwI+BrNuurbvqZ0v3J1DjqhglKdo8KhqgBchIcKVHlXpbiUABASa8SGiFkg86r hKietZsY0NMaxtLEWNBehobXkJ7THfX0dp2THdtMcMrScIGcV8SJ3JOQa24Gr7/a 0Yh3WQ0ByACsgVzeNqWyLTTVM+yLpe7bZY/bXCY0wju3HmflSh1wizypibgYoehy RuQ4gFOT30B6JtV11texOu0519hshR7RRO8/Cnvd9Nxpuk3oKQMto3NnHskDupTy NvU0jFJWJZuw6QuCFeu8y73I3VZsFtt2kpEia06Fkp5KUeYoLuYdiy1DJSpJ54rO aemTpbcdLzhSpYB592azqXb4LVJjcWtepoyFuT24EhQJbW4raCPjVVvTXEi2KC7H fWpTQOQhuWOfyNc9S6alSocdERxvLbQHZ5x3UuZdovVrfUnMhtSeeW3VAeVdX55Q SoWTkaCtYcXbIf6balPJHeqPvHik1KWcLWeqbdj0e/T07fwqc3DzqV2rU5Q1buvB 27/61ZZ1seUeZQSUjwNdmdB8Or3lVo1euKR0S+ACD8Tg0LXDhhqSAD2lskJA6lKd w8qwXdNTWge0bdSR3qQRUJsY02eF+q4Z7TT+tmnwPYCZZTy8xXcucbbA0rITNab5 5IS6VD60oEQrlDI7JTiccxsUR9K3ImutZ24jsL1OTt5AKIUB8iKL+gMVjjDri1DF 70uHUj2trS0H6EVoNcbtLTQGLzpp5onkr1EOJH0NBcfjdq5hARKEGYMYIeYxnwq5 /O1ZZ5AvGh4MknkVtYSfMUcPoQaNXbhJqJ1RHZsLCeYKVNj+GawdRWrhkwyosXl1 C8cg0O0FC98uWjZbW+xWR+3LUMrC1ZBPwzQJOeKlHCuVLgZoT3bMy4oRHFuozyUp OKzFzImSEIPhVI868EcqmwLReRjlyriXjzAUarkV+YxStiOoWrPWr8d9SU4x1rMS o5ruw8UHnSsCy8oEnNVuSTXVSt9cVc81AzwtQFeAoEYr8Uk13jWybLGWI61j3imA ZaZ15frRFTFtMOOpLY5nYSfnRAnjRqhsqZejRVFQKSkJINBMDTV7RkMvNR9/tZdA 8a37NplMO4tvXCZGddChgBeR86ylGF2bwUgcuF4fmyVuPNFC1nOMUccN9NremouU xshA5oCh1o/i6J07dlJlLDQdT7iMGtdyK1a2ihpaNgGBisZyVcGqg75Mma4hUlY6 AHArLkutYUlaQoHkcjNWXlJWpSveay5Ccg1y92dCjFoxpOl7XOJKNzSj+7Uq+kba lbLLNL2T4ofAgPGq82xYZvOj5QVj11NhScfIir0fjVoa5fdzobrGR6weYBxS5h8b dVsL/pkeFNT0wtvBHzrRHFTTN1bS1e9FRSScrW1jr7x316NnmjBRO4UaiSdki3Nu dM7i0oV7PDHR1yRmDPPPoW30rpdF7g/d3Cl6JKtqnBjcknamu0bQujpCkqsGvFsn PJLi8YPlQARTOBSVFRj3Ftz3BaMGhu4cGr1CSVtxkyAATlpYOPlWn/JLiNbQfsPW SJrecpSqRzPyOfrXh3U/F/T8VX2lbWZDOMF8pB2/nlJpgLG4xXoC1NOoKFJ5EK7q HJCiSTmiG83GXcHXHpLaUuKOVbffQw6SQakDzvIr938q2NFNtv63sjT7aHWlzWgp CxlKhuHIjvpt37R9tsFj1/cXbew416cwYqSkDa0VJUoIP4QdxTy91ACL3ipuB76Y XEfTundNW6Gm1t7pFxeXLZX2hV2cQgbE4z1yTz68qM5llYnTNGWiRbLOLJOaih4t JQiWtzsio5I9bacde+mIRYFegnnTAl6Xs7T2hEojKAurq0zPvD64D+wfD1fdRL/I 6wp1zNtcjTAjFmOtVviLuCv6wIcxuznIO0EhPfSATyT+dRQpjapg2iDw4kqtcUoQ jUbrLTj7W14NhAwhRPPkc8jS3S4D1ooZ4UMV0ZmSWB906pIHurQtdqN1e2B1Lae9 Ro4h6D0+ljfLnOKPeQqpbSGrvgXv2lKOSt5XPrRBYrNerwntokd1TY/FjkaY1k0x ouK+hSWRJcTz+9Oc/KmfBuVqjMJS00y0hI5JSkACsJzXRunJdiqtFm1LD2FSFNtj qSegrbkzZO7sXcnbyye+u2stdNP3GLZba6kekLCVrT3flWlqKGiMY45EloEn3nFZ ODfJe/0wd+U1VfOBX4t7aoiuEiW20yVLIz3CsXFmsZ8HNaxipWSJDqySrlk1KFFj 2C248IYTx322YUj91xOfMUNS+Et5aUezaafT70LA+tSpXrHmmHK4fXdhtRVbpHLq Nmaw5GmpzRG6G8g92Wz/AAqVKQzmY11iOhSXZjSxzBQtSavjU+qWoS4artNVHUMK QslWR8TUqUwMeRIedQd6VEn/AGTWWpClE5Qv/CalSpAu2KabNqC33Mx1upiSEPFs ct205xnuo0vnE2TfNPy7U7bnEh5jsQsuZ2ntu0yRjnywn5VKlAApqK8rvwtYERbP oMBuHzOd+0n1unLr0rZTrYjWNiv32a5i1RmWC1v5ubElOc45ZzUqUxFlOt4C4FjT JsUlybZ1lTDyZG1PN3tDlO3n7q6J1tZRqOZczpqUUTgVPhUnc4hztN4U2op9Tpj4 GpUoAydR6rGooUxCre+zIk3Fc0kPKLaQRjbs6Z5e1QqELH4Ff4TUqUAdG1vtf2fa JP5A13E+4AFPbPEe7nUqUmkB2j3a5RXN7bjoPwNao1TdHWihal59+DUqVOqKtmjo uFJumrGH1hZDZzkg9c06dXysPMN7cqDfM4qVKJJAm7AKU+pJOEq8KznXVOe0lRx+ VSpXM0joi2cys4xtOfhUqVKii7P/2YkCNgQTAQoAIAUCZ0teqgIbAwULCQgHAwUV CgkICwQWAgEAAh4BAheAAAoJEEp1iDzBsdNMxsoP/2amun27Yf9/9lXVZJUagfkm 5M4dBPDoC5YfR7IQ1kFjvexC5vSEQRcD8w/hxyrAlqdYOZqZ8K30S8DS5XFlo0DV O/UXSiglaaTHpZIBkiZwutB5BJA1BzGdj0CsQZnOc2lVaJQoZg29k1TBFvinO1tQ t5o2ue4GMg20CjNjDG7QmQ+Dex1rNSIlbusEPeNybyLZVoRsAEAWirwZ2khAwuxo S+EUs3hTRTXVuhg0Ed9zL4nvV3f8WiUoK0fTHLj5Esx8DBiB/IXZCGGRZziORupe xeugX7kOx5eRpmok7rxZIPIUEfBpC5Zr0EysVa6lh9b6U11eDPFZfNkIUAYJboj7 MvvvJkviA8kg8xEo4oe2eMrwOvMKnpPq0xtsOesmdT4iXREEAbndlnOm9L7o1lIn ZvH7fk3K+myDryh/JejgUNiz/Vk8s8JBCsD8vb9P0TdkG8Jy07VoiTcKdDjaNj9T dqjXq280OYwb8KprhdQmfSMfVhqOa3X0N5xFxIPutOZHYILenAbLQ9GXpNVhCshm ApW8F0cHqoPJXLyIyAQQRgib2zmUfY8aZCgxd5C08HOZMfnY2vdoYZ+tchVoHGIR mpo4RlLFY9ZF6NQW9c+bXJqVXpFNJqtRc2O7YZCs2HzisaudBnx1aFbz2HLDzSU3 ybKi93/CIASzyBkzVpLtuQINBFav2jMBEACxwOSaz5YrOdJ2pp3L/8454ACGhRGX YzKtNgj9gPNT6GyJDHW+x61TN1AeR13MqM5UaIvMrjhE17bh62LhkpBEvg2cRrYB Ge7r8J/8E0Q1i/FeFnjS7PeAGOmT32krDtz0GhcRYoTh6uWBIb3aiYYyU5dufit5 ObSjS3qWHRBdIr2Pie6/ppLOVXdeDsbtscU63HkujRMljYd4uPR6oJwFgdQbySK9 tKU/HUS3qhX8SJ6hEN6rfuzEONWynN36ofDS74W2srZxXF5rz7XxYMUe27+9sZd0 zlgTmXL+3wcUfyCTfr3ZxZdx0FL8GY53OrZDQmSCyY667133O/EzVdBLH5vY1I9u d1H2PxoDPQacjl36/mRCpKNGs2Oh52B3NbJ5U7YeEG4OMcA1zC2blih9ExRhi3gD KFcpTXklvJPPS4ffIurdYFTkcWa8Ko+Ck+RHEOl3qXAINrQk9B5M2+eK3SBt5vC8 L/+Ke0ah3vpkuLUV2Piimtgw38eoDw/H/3v+vQ6O5mYLTCqY59c84HZw2NWGaJdX gHZpr2DlwuEMCQkwPWUt53r+8/Sru4LaDjsJv2V6MNTTeYB9e4LfWwZhHA1Us3SU 4A47B5MpNmTXmBxVLfX0qVJfrs0c5726F16cuAqpL8pOQ5+O/UPQ9+F2l/1h3lxK w0I0ZBq4tOqhzQARAQABiQIfBBgBCAAJBQJWr9ozAhsMAAoJEEp1iDzBsdNMGugP /05GhajYg4ES54fn8lcbvnkGm1w5NVP7OS9wzGY/6nDTHX8rmMvVFBYQXerCBZEo IihXPBTuvQ3vYfXnfwglyRw6QvepLM3oez0iLLJPjQU25SgXutl2EIjVbzYtcmkX DGhUGi7IHSqmjIQumrTQWbHzyUAA58otUh4aPYl4aAKxCOMSJlqzUnOmkZRFIynC 6zxHZvh68G2bv503w7R0S867fjO7qnckRMQI7+MYRfWvTdiwqtw+0dKUkTDhkHIz 4sHHZmWISUXhC1kIA9BoxxVXddL5GoAde0L/62cSXL7HDt1tkA0hhO17is1wu3sm lLUeTvsL7LfXI3bOIQjY1CdlNyf65utFnvFsNNVav2ZEXGYcZH2uvKgY/quIa1+y Cbf8w/aYt+ahoi54NAldvoXE6EPs+bZuDviGLHXCLfQLuMu7NfJyJEkPbxLMf+58 k/bkZ8r7vC+x3EpRSI7oHaYYtoQDsRN2NIrRYwuCXlLt26dIGmmdbzLT5bribw7Q CZYkhjd9jnV7+dpAcVTVrE+A7AXb46JVvFaKrhl6rPIlcB81+XoSg4hvAJOWPvcZ CfWrtHVGvPzOJpNxBQteoYUc1SrVi/1j5WR+FnVDA68pY5QdK3fNSDXIhctNxMxC Yv5/cxSTVRCsTbtFg8tRHkJHhq4FVIk0O8o+TSVrfxzs =JPry -----END PGP PUBLIC KEY BLOCK-----
-
 @ 005bc4de:ef11e1a2
2025-05-12 14:00:42
@ 005bc4de:ef11e1a2
2025-05-12 14:00:42Hostr
Hive + Nostr = Hostr, a bidirectional bridge.

Hostr is a bidirectional bridge between Nostr and Hive. What you post on one is automatically cross-posted to the other. (See SETUP.md if you want to jump right in and run it.)
This is experimental. Expect that there will be glitches, errors, and corrections to be made. So, consider it very beta, with no guarantees, and use at your own risk.
Nostr and Hive have differences, mainly, Nostr is a protocol and Hive is a blockchain. Nostr does not have a token, although bitcoin is much-loved and used across Nostr. Hive has two main tokens: HIVE and the HBD stablecoin. More importantly, Nostr and Hive have similarities. Both are decentralized and censorship resistant thanks to users owning and controlling their own private keys.
Nostr users - why you might want to bridge to Hive
I feel the #1 reason a Nostr user might wish to use this bridge is to permanently store and chronicle your Nostr notes.
-
Immutability for your Nostr notes. Your notes on Nostr are held on relays; if they go away, your notes go away. (There was a “nosdrive.app” backup, however I do not believe it’s still working.) Hive is immutable. There is no "delete" and even an “edit” on Hive does not erase the original. Like with a wiki page, a Hive edit shows the most recent version, but the original still remains historically. This would give Nostr users a permanent record of their notes in chronological order.
-
Hive is an excellent long form blogging platform with stable and persistent links. Finding old Nostr notes can be difficult.
-
Increase your reach and potentially gain followers. Your content will bridge off of the Nostr island and be opened to 10-30,000 daily Hive users. Go to https://peakd.com/c/hive-133987 and look for “Hive statistics” to see numbers.
-
Earn rewards in HIVE and HBD. “Likes” on Nostr do not reward you monetarily, but every upvote on Hive yields rewards. For bitcoin maxis, these tokens can easily be swapped into sats with tools like the https://v4v.app web app, or others.
-
Help grow Nostr. Every note that bridges over to Hive will have a footer saying something like, “This note originated on Nostr,” with a link back to your Nostr note on njump.me. On that page, a "Join Nostr" button is prominent.
Hive users - why you might want to bridge to Nostr
-
Increase your reach and potentially gain followers. Your content will be bridged off the Hive island and be opened to 17-18,000 daily users. See https://stats.nostr.band for Nostr stats.
-
Earn bitcoin sats in the form of “zaps.” Nostr does not have a token. But, it has a strong culture of zapping (tipping) bitcoin satoshis to other users to reward quality content. Memes are loved and often zapped too.
-
Unlimited posting. Nostr is not held back by posting or activity limitations, such as with Resource Credits or community norms that frown on posting too often.
-
Even more censorship resistance. Hive is truly censorship-free in that posted content, no matter the content, does indeed posted. However, front ends can choose to show or not show content that the community has downvoted. Nostr is more free speech or censorship resistant...you post it, it's posted. (Relays can choose to relay it or not, accept it or reject it, but you could run your own relay.)
-
Help grow Hive. Every post that bridges over to Nostr will have a footer saying something like, “This post originated on Hive,” with a link back to your Hive blockchain post. This brings wider exposure to Hive.
Quirks about Nostr and Hive
If you’re unfamiliar with Nostr, it has a few quirks:
-
You have one private key, called an “nsec”. It goes along with your “npub”, your public key. Your npub is your username, your nsec IS your account.
-
You simply need an nsec, then a “client” which is a front end.
- You need to add “relays” to your client in order to connect. This is very easy, but how to do it depends on the client. Client's usually walk you through this when you start.
- Short form content (like the old "Tweets") are called kind 1 notes. Long form notes, like most Hive posts, are called kind 30023.
If you’re unfamiliar with Hive, it has more quirks:
-
Hive has five private keys, yes, five. Each has a specific purpose. From least powerful to most powerful, they are: posting key (to post), active key (to move tokens), owner key (to do anything), memo key (to dm/pm), and backup/master private key (to totally restore all keys). Don’t worry about all the keys. For Hostr, we only deal with posting notes/posts, so the posting key is all we deal with.
-
Hive has a culture of frowning on posting too often. Doing so can be seen as trying to milk the HIVE/HBD rewards that you gain from upvotes. Too much posting can be viewed as spamming and result in downvotes (this hurts your Web-of-Trust score, called “reputation” on Hive, and is shown alongside your username; you want to grow and keep your reputation up). The chain also has a 5-minute cool-down rule coded in: after posting, you cannot post for another five minutes.
-
Additionally, to avoid spam, Hive actions burn “Resource Credits” or RCs. Think of RCs as the charge % in your phone battery. Every action on Hive uses RCs, so they dwindle with every use. Posting is high in RC cost. Bad news: if you run out of RCs, you’re unable to do things on Hive. Good news: RCs also recharge. If out of RCs, you can wait and then do things later. For the Hostr script, over-posting means the script will post until RCs are exhausted, then it will stall until RCs are recharged, post again, stall, etc. You can check your RCs in many places, such as a Hive explorer like https://hivescan.info and entering your Hive username. If you have RC issues, reach out for help.
You don't want to over-post on Hive. To avoid over-posting, Hostr has two versions of the script:
-
bidirectional-longform30023.js
- Nostr ➡️ Hive - Listens only for kind 30023 (long form) Nostr notes to bridge over to Hive. Kind 1 short form notes are ignored.
- Hive ➡️ Nostr - Any Hive post over 380 characters gets truncated as a kind 1 (short form) Nostr note (with a link back to the full Hive post).
-
bidirectional-bridge.js
- Nostr➡️Hive - This script listens for both kind 1 (short form) and kind 30023 (long form) Nostr notes and bridges both over to Hive.
- Hive ➡️ Nostr - Same as above (380+ is truncated).
Which script version should I use?
- If you post frequently on Nostr (more than 2 times per day?), the bidirectional-longform30023.js script is likely best. Per Hive community norms, you don't want to post too often on there. With this script version, only long form notes will bridge over from Nostr to Hive.
- For newcomers to Hive, I would start with this script to be safe.
-
If in doubt, use this script.
-
If you post infrequently on Nostr (2 times per day or fewer?), the bidirectional-bridge.js (both kinds 1 and 30023) might work fine for you.
Nostr users - how to begin
You’ll need a Hive account. You can see sign-up options at https://signup.hive.io. Some options are free, others are not. I (crrdlx) have some free “VIP tickets” to sign up with and you are welcome to use one if you wish, see https://crrdlx.vercel.app/hive-vip-ticket.html. If the tickets there are already spent, contact me and I'll get you set up.
As with Nostr, the critical thing with a Hive account is saving your keys. Hive has multiple keys, just save them all. We’ll only use the “posting key” for the Hostr bridge, however. The other keys can be used on Hive if you wish. (For instance, the "active key" is used to handle your HIVE/HBD rewards earned, the "memo key" for private messages.)
Once signed up (and keys are safe), you can adjust your Hive account/profile using any Hive front end like https://peakd.com/username, https://ecency.com/username, or https://hive.blog/username. Just remember, every action on Hive burns RCs, keep an eye on that.
You can learn more about Hive at https://hivewiki.vercel.app if you wish.
See the "Setting up..." section below to set up the bridge.
Hive users - how to begin
You’ll need a Nostr account. Getting a Nostr "account" is nothing more than generating keys. A simple way to do this is at https://nstart.me If you wish to dig into details, take a look at http://nostrwiki.crrdlx.infinityfreeapp.com/doku.php?id=wiki:get-started
As with Hive, you simply need to safely store your private keys. On Nostr, your private key is called your “nsec” (sec, as in “secret”). Your public key is your “npub” (pub, as in "public"). Your nsec is all you need, but just so you know, your private key comes in two formats: (a) your nsec, and (b) the “hex” form (same key, just different forms). With the Hostr bridge, we’ll use the hex private key. Depending on how you join Nostr, your hex key may be given to you at sign up. But, even if it's not, you can always check back-and-forth between nsec and hex keys using a tool like https://nostrtool.com and choosing "Load a privkey from nsec/hex".
Again, just save your nsec and/or hex private key and you’re set.
You can learn more about Nostr at https://nostrwiki.vercel.app if you wish.
See the "Setting up..." section below to set up the bridge.
Setting up the Hostr bridge
To set up the bridge, see SETUP.md in the repo below. The Hostr bridge has a bit of technicals behind it, but don't get intimidated. Because technical things change, I’ll keep the technical how-to instructions housed at https://github.com/crrdlx/hostr
Disclaimer
This is an experimental bridge. Expect that there will be glitches, errors, and corrections to be made. So, consider it very beta, with no guarantees, and use at your own risk. Source code: https://github.com/crrdlx/hostr
Built with ❤️ by crrdlx
Connect on Hive: @crrdlx
Connect on Nostr: nostr:npub1qpdufhjpel94srm3ett2azgf49m9dp3n5nm2j0rt0l2mlmc3ux3qza082j
All contacts: https://linktr.ee/crrdlx
-
-
 @ d360efec:14907b5f
2025-05-10 03:57:17
@ d360efec:14907b5f
2025-05-10 03:57:17Disclaimer: * การวิเคราะห์นี้เป็นเพียงแนวทาง ไม่ใช่คำแนะนำในการซื้อขาย * การลงทุนมีความเสี่ยง ผู้ลงทุนควรตัดสินใจด้วยตนเอง
-
 @ c1e9ab3a:9cb56b43
2025-05-09 23:10:14
@ c1e9ab3a:9cb56b43
2025-05-09 23:10:14I. Historical Foundations of U.S. Monetary Architecture
The early monetary system of the United States was built atop inherited commodity money conventions from Europe’s maritime economies. Silver and gold coins—primarily Spanish pieces of eight, Dutch guilders, and other foreign specie—formed the basis of colonial commerce. These units were already integrated into international trade and piracy networks and functioned with natural compatibility across England, France, Spain, and Denmark. Lacking a centralized mint or formal currency, the U.S. adopted these forms de facto.
As security risks and the practical constraints of physical coinage mounted, banks emerged to warehouse specie and issue redeemable certificates. These certificates evolved into fiduciary media—claims on specie not actually in hand. Banks observed over time that substantial portions of reserves remained unclaimed for years. This enabled fractional reserve banking: issuing more claims than reserves held, so long as redemption demand stayed low. The practice was inherently unstable, prone to panics and bank runs, prompting eventual centralization through the formation of the Federal Reserve in 1913.
Following the Civil War and unstable reinstatements of gold convertibility, the U.S. sought global monetary stability. After World War II, the Bretton Woods system formalized the U.S. dollar as the global reserve currency. The dollar was nominally backed by gold, but most international dollars were held offshore and recycled into U.S. Treasuries. The Nixon Shock of 1971 eliminated the gold peg, converting the dollar into pure fiat. Yet offshore dollar demand remained, sustained by oil trade mandates and the unique role of Treasuries as global reserve assets.
II. The Structure of Fiduciary Media and Treasury Demand
Under this system, foreign trade surpluses with the U.S. generate excess dollars. These surplus dollars are parked in U.S. Treasuries, thereby recycling trade imbalances into U.S. fiscal liquidity. While technically loans to the U.S. government, these purchases act like interest-only transfers—governments receive yield, and the U.S. receives spendable liquidity without principal repayment due in the short term. Debt is perpetually rolled over, rarely extinguished.
This creates an illusion of global subsidy: U.S. deficits are financed via foreign capital inflows that, in practice, function more like financial tribute systems than conventional debt markets. The underlying asset—U.S. Treasury debt—functions as the base reserve asset of the dollar system, replacing gold in post-Bretton Woods monetary logic.
III. Emergence of Tether and the Parastatal Dollar
Tether (USDT), as a private issuer of dollar-denominated tokens, mimics key central bank behaviors while operating outside the regulatory perimeter. It mints tokens allegedly backed 1:1 by U.S. dollars or dollar-denominated securities (mostly Treasuries). These tokens circulate globally, often in jurisdictions with limited banking access, and increasingly serve as synthetic dollar substitutes.
If USDT gains dominance as the preferred medium of exchange—due to technological advantages, speed, programmability, or access—it displaces Federal Reserve Notes (FRNs) not through devaluation, but through functional obsolescence. Gresham’s Law inverts: good money (more liquid, programmable, globally transferable USDT) displaces bad (FRNs) even if both maintain a nominal 1:1 parity.
Over time, this preference translates to a systemic demand shift. Actors increasingly use Tether instead of FRNs, especially in global commerce, digital marketplaces, or decentralized finance. Tether tokens effectively become shadow base money.
IV. Interaction with Commercial Banking and Redemption Mechanics
Under traditional fractional reserve systems, commercial banks issue loans denominated in U.S. dollars, expanding the money supply. When borrowers repay loans, this destroys the created dollars and contracts monetary elasticity. If borrowers repay in USDT instead of FRNs:
- Banks receive a non-Fed liability (USDT).
- USDT is not recognized as reserve-eligible within the Federal Reserve System.
- Banks must either redeem USDT for FRNs, or demand par-value conversion from Tether to settle reserve requirements and balance their books.
This places redemption pressure on Tether and threatens its 1:1 peg under stress. If redemption latency, friction, or cost arises, USDT’s equivalence to FRNs is compromised. Conversely, if banks are permitted or compelled to hold USDT as reserve or regulatory capital, Tether becomes a de facto reserve issuer.
In this scenario, banks may begin demanding loans in USDT, mirroring borrower behavior. For this to occur sustainably, banks must secure Tether liquidity. This creates two options: - Purchase USDT from Tether or on the secondary market, collateralized by existing fiat. - Borrow USDT directly from Tether, using bank-issued debt as collateral.
The latter mirrors Federal Reserve discount window operations. Tether becomes a lender of first resort, providing monetary elasticity to the banking system by creating new tokens against promissory assets—exactly how central banks function.
V. Structural Consequences: Parallel Central Banking
If Tether begins lending to commercial banks, issuing tokens backed by bank notes or collateralized debt obligations: - Tether controls the expansion of broad money through credit issuance. - Its balance sheet mimics a central bank, with Treasuries and bank debt as assets and tokens as liabilities. - It intermediates between sovereign debt and global liquidity demand, replacing the Federal Reserve’s open market operations with its own issuance-redemption cycles.
Simultaneously, if Tether purchases U.S. Treasuries with FRNs received through token issuance, it: - Supplies the Treasury with new liquidity (via bond purchases). - Collects yield on government debt. - Issues a parallel form of U.S. dollars that never require redemption—an interest-only loan to the U.S. government from a non-sovereign entity.
In this context, Tether performs monetary functions of both a central bank and a sovereign wealth fund, without political accountability or regulatory transparency.
VI. Endgame: Institutional Inversion and Fed Redundancy
This paradigm represents an institutional inversion:
- The Federal Reserve becomes a legacy issuer.
- Tether becomes the operational base money provider in both retail and interbank contexts.
- Treasuries remain the foundational reserve asset, but access to them is mediated by a private intermediary.
- The dollar persists, but its issuer changes. The State becomes a fiscal agent of a decentralized financial ecosystem, not its monetary sovereign.
Unless the Federal Reserve reasserts control—either by absorbing Tether, outlawing its instruments, or integrating its tokens into the reserve framework—it risks becoming irrelevant in the daily function of money.
Tether, in this configuration, is no longer a derivative of the dollar—it is the dollar, just one level removed from sovereign control. The future of monetary sovereignty under such a regime is post-national and platform-mediated.
-
 @ c3e23eb5:03d7caa9
2025-05-12 13:00:36
@ c3e23eb5:03d7caa9
2025-05-12 13:00:36The issue I have with the term "mesh networks" is that it is associated with a flat network topology. While I love the idea of avoiding hierarchy, this simply doesn't scale. Data Plane: How the Internet Scales
The internet on the scales because it has a tree like structure. As you can see in the diagram below, global (tier 1) ISPs branch out to national (tier 2) ISPs who in turn branch out to local (tier 3) ISPs.
``` ,-[ Tier 1 ISP (Global) ]─-───────[ Tier 1 ISP (Global) ] / |
/ ▼
[IXP (Global)]═══╦═══[IXP (Global)]
║
Tier 2 ISP (National)◄──────────╗
/ \ ║
▼ ▼ ║
[IXP (Regional)]════╬══[IXP (Regional)] ║
/ \ ║
▼ ▼ ║
Tier 3 ISP (Local) Tier 3 ISP (Local) ║
| | ║
▼ ▼ ▼
[User] [User] [Enterprise]▲ IXPs are physical switch fabrics - members peer directly ▲ Tier 1/2 ISPs provide transit through IXPs but don't control them ```
This structure also reflects in IP addresses, where regional traffic gets routed by regional tiers and global traffic keeps getting passed up through gateways till it reaches the root of the tree. The global ISP then routes the traffic into the correct branch so that it can trickle down to the destination IP at the bottom.
12.0.0.0/8 - Tier 1 manages routing (IANA-allocated) └─12.34.0.0/16 - Tier 2 allocated block (through RIR) └─12.34.56.0/24 - Tier 3 subnet via upstream provider ├─12.34.56.1 Public IP (CGNAT pool) └─192.168.1.1 Private IP (local NAT reuse)Balancing idealism with pragmatism
This approach to scaling is much less idealistic than a flat hierarchy, because it relies on an authority (IANA) to assign the IP ranges to ISPs through Regional Internet Registries (RIRs). Even if this authority wasn't required, the fact that many users rely on few Tier 1 ISPs means that the system is inherently susceptible to sabotage (see 2019 BGP leak incident).
Control Plane: the internet is still described as decentralised
The internet is still described as decentralised because there is a flat hierarchy between
tier 1ISPs at the root of the tree. ``` INTERNET CORE (Tier 1 ISPs)AT&T (AS7018) <══════════> Deutsche Telekom (AS3320) ║ ╔════════════════════╗ ║ ║ ║ ║ ║ ╚══>║ NTT (AS2914) ║<══╝ ║ ║ ║ ║ ║ ║ ╚═══════> Lumen (AS3356) ║ ║ ╚════╩════════════> Telia (AS1299)
```
The border gateway protocol (BGP) is used to exchange routing information between autonomous systems (ISPs). Each autonomous system is a branch of the "internet tree" and each autonomous system advertises routes to downstream autonomous systems (branches). However, the autonomous systems at the root of the tree also maintain a record of their piers, so that they can forward traffic to the correct peer. Hence, the following is a more complete diagram of the internet: ```
INTERNET CORE (TIER 1 MESH) ╔══════════════╦═════════════╦════════╦═════════════╗ ║ ║ ║ ║ ║ AT&T (AS7018) <══╬══> Lumen (AS3356) <══╬══> NTT (AS2914) ║ ║ ║ ║ ║ ║ ║ ╚══> Telia (AS1299) <══╝ ║ ║ ╚═══════════════════════════════╝ ║ ║ ╚═> Deutsche Telekom (AS3320) <═╝ ║ TREE HIERARCHY BELOW - MESH ABOVE ║ ▼ [ Tier 1 ISP ]───────────────────┐ / | | / ▼ ▼ [IXP]═══╦═══[IXP] [IXP] ║ ║ ▼ ▼ Tier 2 ISP◄──────────╗ Tier 2 ISP◄───────╗ / \ ║ / \ ║ ▼ ▼ ║ ▼ ▼ ║ [IXP]═╦[IXP] ║ [IXP]═╦[IXP] ║ / \ ║ / \ ║ ▼ ▼ ▼ ▼ ▼ ▼ Tier 3 ISP User Tier 3 ISP Enterprise```
So its a mesh network - whats wrong with that?
In the example above, NTT can only send traffic to Deutsche Telekom via Lumen or AT&T. NTT relies on its peers to maintain a correct record of the IP range that they are responsible for, so that traffic that was intended for Deutsche Telekom doesn't end up in the wrong network. An intentional or even accidental error in an autonomous system's routing tables can be detrimental to the flow of traffic through the network.
Hence, mesh networks require: * Reliability: peers rely on each-other not to fail (e.g., 2019 AWS US-East-1 availability) * Trust: peers must be honest about address ranges (e.g., 2018 BGP hijacking incident) * Central planning: BGP traffic engineering determines which route a packet takes
Application Layer Innovations
Now that we have a rough overview of how the internet is broken, lets think about what can still be done. The flat hierarchy that we associate with mesh networks sounds beautiful, but it doesn't scale. However, the tree-like structure assumes that most participants in the network rely on an authority to give them an address or a range of addresses so that they can communicate.
Overlay networks
Fortunately all it takes to interact with someone on nostr is their public key. The recipients client will render your signed and/or encrypted event no matter how it reaches them. Whether your note reaches them over the internet, over some other network or via a carrier pigeon doesn't matter. nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr is working on a NIP for that and I'm sure he will share an explanation of how it works.
Bitcoin Instead of a Routing Algorithm
Now that we have digital bearer assets (e-cash), users can pay their internet gateway (TollGate) for access to the internet even though they are still offline. Once the TollGate has redeemed the e-cash, it gives the user access to the internet.
Frictionless Switching between ISPs (TollGates)
Legacy internet service providers use KYC money (fiat) to transfer the cost of the infrastructure to their users. However, this means that they are able to identify which packet belongs to which user. The KYC nature of their interaction with the users also makes it difficult for users to switch ISPs when service providers undercut each-other. Internet users who are on e-cash rails can hop between ISPs frictionlessly since they buy small amounts of data frequently in a granular manner.
Users that have access to independent competing TollGates can switch between them freely, so its impossible for any one TollGate to prevent a user from connecting to the internet. The only thing a TollGate can do is attract traffic by providing cheaper and/or faster internet access.
Anyone can arbitrage connectivity
Now that users have non KYC internet, there is nothing stopping them from reselling access to their internet connection. Anyone who has a WiFi router and access to a cheap internet connection can act as a range extender by re-selling access to that gateway for people who aren't able to connect directly.
Now the route that the traffic takes through the network is determined dynamically by the markets. The individual TollGate operators select their gateways and set their prices when they create a business model. The customers select the route that best meets their needs by selecting a gateway for their next purchase.
-
 @ a3c6f928:d45494fb
2025-05-12 15:30:48
@ a3c6f928:d45494fb
2025-05-12 15:30:48Financial freedom is a powerful concept—one that goes beyond simply having money in the bank. It is the ability to live the life you desire, free from the constraints of financial worry. Achieving financial freedom requires planning, discipline, and a clear understanding of your financial goals.
What Is Financial Freedom?
Financial freedom means having enough income, savings, and investments to support the lifestyle you want for yourself and your family. It is about being in control of your finances, instead of your finances controlling you. When you are financially free, you have choices—you can travel, start a business, or retire comfortably without constant stress about money.
Steps to Achieving Financial Freedom
-
Set Clear Financial Goals: Understand what financial freedom means to you and set measurable goals to achieve it.
-
Create a Budget and Stick to It: Track your income and expenses to identify areas where you can save more.
-
Invest Wisely: Grow your wealth by investing in assets like stocks, real estate, or mutual funds.
-
Build an Emergency Fund: Save at least 3-6 months’ worth of living expenses to protect against unexpected events.
-
Eliminate Debt: High-interest debt can be a major barrier to financial freedom. Prioritize paying it off.
Why Financial Freedom Matters
Financial freedom gives you the power to make decisions without being bound by financial constraints. It allows for greater life flexibility, reduces stress, and opens up opportunities that would otherwise be unreachable. Most importantly, it provides peace of mind and the ability to focus on what truly matters.
Start Your Journey Today
The path to financial freedom is not a quick fix—it is a lifelong commitment to smart financial choices. But with perseverance and planning, it is achievable. Begin today, and take control of your financial future.
“Financial freedom is available to those who learn about it and work for it.” — Robert Kiyosaki
Plan wisely. Invest smartly. Live freely.
-
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ cecdc1e8:b6c264ee
2025-05-12 12:41:57
@ cecdc1e8:b6c264ee
2025-05-12 12:41:57GM
-
 @ 7460b7fd:4fc4e74b
2025-05-12 12:23:54
@ 7460b7fd:4fc4e74b
2025-05-12 12:23:54警惕:那些“帮你”保管密钥的人
—— 多签钱包中的隐形风险与逻辑陷阱
“我们可以帮您设置一个更安全的钱包。” 这句话,听上去就像是关心,其实却可能是一次有预谋的接管。
摘要
多签钱包被广泛视为提升数字资产安全性的“进阶方案”,尤其适用于不希望将所有信任寄托于单一点故障(如一把私钥)的人群。然而,在这些看似“民主化”、“抗单点失败”的技术结构背后,仍潜藏着极为隐秘且被低估的风险。
本文聚焦两类常见却高度隐蔽的逻辑攻击模型:
- 替换 xpub 并接管下一层级地址生成;
- 伪造
k-of-n多签结构,在形式上给予用户参与感,实则实现单人提款。
在未引入 Taproot 的传统多签结构下,这类攻击已能轻易完成。而即便在 Taproot 和 MuSig2 合约模型下,攻击者也可以借助合成结构进一步隐藏其篡改行为。
本报告不仅梳理攻击逻辑,更强调“人性中的信任误区”——攻击者不需要主动索取密钥,只需要维持友善形象,自会有用户主动递交钥匙。更令人警惕的是,在某些极端场景下,这类“被信任的服务商”甚至可能向受害者收取“保管密钥”的费用后再实施盗窃,形成双重获利。
Taproot 虽然在结构上增强了隐私与复杂性,但也使验证逻辑失去了可直观还原的优势。随着时间推移、服务厂商退出市场乃至私有恢复流程被锁死,用户极可能落入无法恢复的“密钥黑箱”中。
阅读本文,希望你能意识到:
真正的安全,从不是托付给别人帮你“多签”,而是你真正理解你签了什么、和谁签的、签名之后将通往哪一个脚本。
多签钱包的逻辑攻击向量分析
以 xpub 替换与伪造 k-of-n 结构为例
攻击模型一:替换 xpub 实现地址劫持
场景设定
攻击者假扮为友好的钱包初始化服务者,主动提出“免费帮你生成一个更安全的多签钱包”。表面上,他为你设置了标准的 HD 多签结构,实际上却在关键的派生路径中,悄悄将本应由你或另一个可信方持有的 xpub 替换为他自己的。
在 HD 钱包结构(例如 BIP45、BIP67)中,用户通常无法直观验证每一个新地址是否仍属于原来的签名组。这种设计让“看上去很安全”的地址,可能早已成为攻击者可完全支配的提款口袋。
攻击结构(逻辑表示)
- 假设多签参与者为
P1, P2, P3 - 攻击者控制伪造者身份
P1',实际替代掉用户的P1 - 地址生成函数为:
Addr = f(xpub(P1'), xpub(P2), xpub(P3))- 用户未验证 xpub 时,成立:
∃ Addr_i ∈ wallet, spendable_by(attacker)换言之,钱包中的某些地址虽然看起来正常,但已可被攻击者花费。
人性陷阱提示
用户往往不认为“地址生成这件事”是需要人工检查的,特别是在使用 Ledger、Trezor 等硬件钱包时形成了“签名即安全”的错觉。而攻击者只需一次替换,就能悄悄监视整个钱包生命周期。
更重要的是,攻击者不需要向你“索取密钥”,他只需维持友善、专业甚至略带“为你好”的姿态。在 100 个用户中,总会有一部分人,在受到“信任感”与“他人看起来更专业”的影响下,主动提出将某个密钥托管给对方,甚至支付一定“密钥保管费”作为安全保障。这类行为并非愚蠢,而是人性的一部分。
这种松懈与依赖,背后深植着心理学上著名的「责任分散效应(diffusion of responsibility)」。当责任从“自己一人持有私钥”转变为“我们多人共同掌控”时,大脑会自动削弱“必须百分百保护密钥”的紧迫感;一旦密钥有三份或五份,人就会默认“即使我丢了一份也无所谓”,由此降低警惕,弱化加密习惯的执行力度。
尤其是在多签结构下,密钥不再是“唯一真理”。你开始认为:“我只是 n-of-m 的一员”,进而产生 安全责任稀释(safety dilution)。举个例子:如果你的 seed words 是唯一的,你很可能将其写在一张专用纸上,藏入防火袋,存放于密封保险箱中;但一旦你拥有的是 3-of-5 多签中的一份,你可能就只是把它存在 Evernote、存图于手机相册,或者发给自己 Telegram 备份——并自我安慰说:“这只是其中一把钥匙,又不怕。”
这正是攻击者渗透的最佳入口。他无需破解密码学算法,仅凭理解人性中的懒惰、依赖与责任下沉机制,就足以发起极具杀伤力的社会工程攻击。
提醒:没有人例外。你的安全不是由数学公式决定,而是由你是否对它持续保持敬畏与冷静判断所决定的。
Taproot 下的隐蔽性升级
在 Taproot + MuSig2 合约结构中:
- 合成公钥如:
P = H(P1 + P2 + P3) - 用户无法从地址推导出其组成
- 所有 pubkey 被掩盖,无任何可读性结构泄露
结果:攻击者替换某个 xpub 之后,哪怕是资深用户,也无法通过比对地址结构来发现任何异常。
攻击模型二:伪造 k-of-n 多签脚本结构
场景设定
攻击者承诺为你部署一个“非常安全”的
2-of-3多签钱包。然而他实际创建的却是一个1-of-3结构,并诱导你保留或交出其中一个密钥。用户一旦信任其脚本不可见性(或 UI 模糊性),资金注入该地址之后,攻击者即可单独提款。
攻击结构(逻辑描述)
- 正确脚本应为:
OP_2 <pk1> <pk2> <pk3> OP_3 OP_CHECKMULTISIG- 实际被构造为:
OP_1 <pk1> <pk2> <pk3> OP_3 OP_CHECKMULTISIG- 用户错误地相信:
user_believes(k=2) ∧ attacker_has(sk1) → safe- 但实际上:
real_k = 1 ∧ attacker_has(sk1) → attacker_can_spend成立条件
- 用户未能验证 redeem script
- 钱包界面(UI 或 PSBT)未明确标识 k 值与脚本结构
- 攻击者拥有脚本定义权,或 UI 权限
人性陷阱提示
这类攻击往往并非“高技术”,而是利用用户对脚本结构的无感。尤其是当攻击者扮演“技术专家”时,用户往往不具备审查 redeem script 的能力或意识。攻击者甚至可以用“给你设置一个冷备密钥”作为幌子,骗取部分 key,并收取额外费用。
多签攻击模型对比分析(无表格)
- 攻击类型一:xpub 替换
- 本质:公钥注入
- 隐蔽性:极高(生成地址完全正常)
- 关键条件:用户未验证每个 xpub
-
Taproot 是否能规避:否,反而更难发现
-
攻击类型二:伪造 k-of-n
- 本质:脚本结构欺骗
- 隐蔽性:中等(需查看 redeem script 才能识别)
- 关键条件:用户不懂脚本,UI 不展示结构
- Taproot 是否能规避:否,合约结构反而隐藏了更多细节
安全建议(基于当前攻击模型)
- 强制在 UI 中完整展示所有 xpub、合成地址派生路径与对应签名人列表
- 如 Coldcard 的二维码验证机制
- 用户必须自行保存每个 xpub,并可验证任一地址确实源自该集合派生
- 多签钱包必须提供可见 redeem script 的界面与 k 值校验提示
- 不接受“帮你配置好了”的 UI 黑箱
- Taproot 虽增强隐私,但也加剧验证障碍
- 若使用合签结构,应避免依赖第三方界面进行签名决策
- 始终优先使用硬件钱包本地签名流程,避免通过 Web 或中间服务生成交易
真实案例分析
1. Coldcard 硬件钱包的 xpub 替换漏洞
2021 年,安全研究员 benma 发现 Coldcard 硬件钱包在注册多签钱包时,未验证自身是否为多签钱包的一部分。这使得恶意计算机钱包可以用攻击者控制的 xpub 替换多签 xpub,同时仍通过所有用户验证。所有接收到此多签钱包的币随后可以随时转移到攻击者的钱包。
来源:benma.github.io2. Bybit 交易所的多签钱包被黑事件
2025 年 2 月,Bybit 交易所的多签冷钱包在一次例行转账中被黑,损失约 14.6 亿美元。该钱包使用 2-of-3 多签设置,意味着需要三位授权签名人中的两位批准交易。用户界面显示了合法的目标地址,并且 URL 与受信任的多签提供商 Safe 相关联。但这是一种欺骗。黑客利用硬件钱包中的“盲签名”漏洞,使设备只能显示交易的哈希,从而掩盖了一个更改,使攻击者控制了钱包的智能合约。
来源:certora.com3. Parity 多签钱包漏洞
2017 年,Parity 多签钱包版本 1.5+ 中发现了一个漏洞,允许攻击者窃取超过 150,000 ETH(约 3000 万美元)。攻击者向受影响的合约发送两个交易:第一个获取多签的独占所有权,第二个移动其所有资金。
来源:blog.openzeppelin.com
攻击流程图解
- 建立信任:攻击者以技术专家或受信任的服务提供商身份接近受害者,提出帮助设置多签钱包。
- 替换 xpub:在设置过程中,攻击者用自己控制的 xpub 替换原本应由用户或第三方控制的 xpub。
- 生成地址:攻击者生成看似正常的多签地址,并展示给用户,用户未进行验证。
- 资金注入:用户将资金转入这些地址,认为资金安全。
- 资金转移:攻击者利用控制的私钥,单方面将资金转出,用户无法察觉。
参考文献
附录:攻击面分析——为何 xpub 替换是多签特有的风险?
单签钱包是否存在 xpub 替换攻击?
答案:否。
在单签钱包结构中(如 BIP32/BIP39 衍生的标准钱包):
- 钱包只依赖一个 xpub,并且这个 xpub 是从用户私钥派生而来;
- Coldcard、Trezor 等硬件钱包会自动根据本地 seed 派生地址,无需输入外部 xpub;
- 用户可以通过设备显示屏确认“这是我派生出来的地址”,不存在外部注入路径。
因此:xpub 替换在单签钱包中不存在攻击面,攻击路径被封死。
多签钱包为什么引入了 xpub 攻击面?
多签钱包(如 2-of-3、3-of-5)需要以下信息来生成地址:
- 所有参与者的 xpub;
- 公钥排序规则(如 BIP67);
- 多签脚本模板(如 OP_2
OP_3 OP_CHECKMULTISIG); - 每个 key 的派生路径(如 m/48'/0'/0'/2'/0/1);
这就意味着,用户必须信任这些输入的 xpub 是来自真正的签名方。如果攻击者悄悄将其中某一份换成自己控制的 xpub,那他就自动成为地址共管人,甚至是单签人。
Coldcard 攻击案例回顾:
- 用户通过 PSBT 模板或 JSON 导入多签配置;
- 攻击者在其中替换了某一参与者的 xpub;
- Coldcard 在旧版本中未提示或验证该替换;
- 用户生成地址、发送资金,攻击者即可随时提取。
攻击面比较表
- 单签钱包
- 不接收外部 xpub,派生路径完全由设备掌控;
- 地址来源明确、签名单一;
-
xpub 替换攻击无效。
-
多签钱包
- 依赖多个外部 xpub 合成结构;
- 用户很难手动验证每一条 xpub 与 fingerprint;
- xpub 替换为高危攻击点。
Taproot 是否规避了 xpub 替换问题?
部分规避,但引入了新的验证难题。
Taproot + MuSig2 等结构通过将多个 pubkey 合成为一个点:
P = H(P1 + P2 + P3)
这确实可以隐藏合约结构,提升隐私,但也导致:
- 用户无法从地址还原参与者是谁;
- 如果其中一个公钥被攻击者替换,生成的地址仍然合法;
- 用户在链上看不到任何异常,但攻击者已取得合约控制权。
因此:Taproot 并未从根本上消除 xpub 替换的攻击面,反而因为其不可还原性使得攻击更加隐蔽。
总结
多签钱包之所以引入新的攻击面,不是因为它“更复杂”,而是因为它必须信任外部结构。一旦你的钱包要“与他人协作生成地址”,你就必须验证“这些人是谁”、“这些地址是怎么来的”——这就是攻击的入口。
单签保护的是私钥,
多签则要求你保护你的伙伴。 -
 @ cb4352cd:a16422d7
2025-05-12 12:18:41
@ cb4352cd:a16422d7
2025-05-12 12:18:41In the early days of the internet, openness was a foundational value. Today, as the financial world undergoes its next great evolution, that same principle is making a powerful return — this time through open-source code, permissionless protocols, and user-owned ecosystems. The future of finance isn’t just digital. It’s open.
Beyond the Institution: A Shift in Trust
Traditional finance has always been built around institutions — banks, central authorities, and regulatory bodies. While these structures offer stability, they also limit access, enforce gatekeeping, and concentrate power.
Permissionless innovation flips this model. Instead of asking for approval, builders create protocols that anyone can use, fork, or improve. In DeFi, anyone with an internet connection can lend, borrow, or trade without relying on a centralized intermediary.
Composability: Financial Lego for the Internet Age
Open protocols don’t just stand alone — they connect. In Web3, composability means developers can build on top of each other’s code like financial Lego blocks. This accelerates experimentation and reduces duplication of effort.
You can build a lending protocol that integrates with a decentralized exchange, which in turn connects to a stablecoin, creating a rich, interoperable financial ecosystem — all without closed APIs or licensing fees.
DAOs and the Redefinition of Governance
Openness is not only about access — it’s about control. Decentralized Autonomous Organizations (DAOs) allow communities to govern protocols, allocate resources, and shape development roadmaps. In contrast to top-down decision-making, DAOs are built on transparency, collective voting, and participatory ownership.
As financial systems move on-chain, governance itself becomes programmable. This allows for more adaptive, responsive institutions that can evolve with user needs — not just boardroom mandates.
More Than Code: A Philosophical Shift
Open finance isn’t just a stack of protocols. It reflects a deeper belief: that financial systems should be inclusive, interoperable, and transparent by design.
This philosophy challenges legacy ideas of exclusivity and control. It opens space for local currencies, niche communities, experimental markets, and user-first financial design. It treats users not as passive consumers but as co-owners and co-builders.
How Beyond Banking Conference by WeFi Embraces Openness
This vision of open finance is a central theme of the Beyond Banking Conference by WeFi. Taking place online on May 30, 2025, the conference brings together pioneers from DeFi, AI, Web3, and FinTech to discuss permissionless technologies, composable architecture, and the human values behind them.
Speakers will explore how openness fuels innovation, and how protocol design shapes access, governance, and trust. From DAOs to AI-powered DeFi, the program emphasizes tools that scale freedom — not just efficiency.
In the future, finance won’t just be smart. It will be open. And that changes everything.
-
 @ 04c915da:3dfbecc9
2025-03-25 17:43:44
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 21335073:a244b1ad
2025-03-18 20:47:50
@ 21335073:a244b1ad
2025-03-18 20:47:50Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 866e0139:6a9334e5
2025-05-12 10:41:33
@ 866e0139:6a9334e5
2025-05-12 10:41:33Autor: Bastian Barucker. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
John Lennon besang in seinem weltberühmten Lied „Imagine“ die fast unvorstellbare Utopie einer Welt, in der es keinen Grund mehr zu töten gäbe und die Menschen in Frieden zusammen leben. Die enorme Resonanz und Verbreitung dieser Zeilen zeigt den Wunsch fast aller Menschen nach Frieden. Wie Lennon zu diesen Zeilen kam, ist ein Hinweis darauf, dass es dazu neben geopolitischen Analysen und deren Verbreitung durch eine nicht eingebettete und freie Presse vielleicht noch etwas braucht: Schattenarbeit – ein bewusstes Hinwenden zu den eigenen Tiefen der Persönlichkeit, dem inneren Tiefenstaat.
Was ist der Tiefenstaat?
Mit dem Begriff Tiefenstaat verbinde ich Strukturen, die Edward Bernays bereits vor knapp 100 Jahren in seinem Grundlagenwerk „Propaganda“ beschrieb. Im Vorwort schreibt er: „Organisationen, die im Verborgenen arbeiten, lenken die gesellschaftlichen Abläufe. Sie sind die eigentlichen Regierungen in unserem Land.“ Er verwendet diesbezüglich auch das Wort „Schattenkabinett“. Im Bereich der Persönlichkeitsentwicklung wird der Begriff „Schattenarbeit“ dafür verwendet, unbekannte, aber einflussreiche Anteile des eigenen Selbst zu entdecken und zu integrieren.
Lennon begab sich in den 70er Jahren des letzten Jahrhunderts auf die Reise zu sich selbst. Sein Weg führte ihn zum Psychologen Dr. Arthur Janov, der Menschen mithilfe der von ihm entwickelten Primärtherapie dabei begleitete, sich ihrer primären Prägungen und frühkindlichen Traumatisierungen bewusst zu werden und abgespaltenen Schmerz wieder zu erleben, um sich davon zu befreien. Entgegen stark kognitiv geprägter Ansätze wie der Gesprächstherapie steht bei dieser Art der Therapie Gefühlsausdruck im Vordergrund. Janov selbst schreibt dazu: «Die Krankheit ist die Verleugnung des Fühlens, und das Heilmittel ist das Fühlen.»
Auch der Psychologe und Psychotherapeut Franz Ruppert beschäftigt sich intensiv mit dem Fühlen als einem möglichen Weg, eine Traumatisierung aufzuarbeiten. Er schreibt Folgendes über die Bedeutung des Fühlens in seinem Buch „Wer bin ich in einer traumatisierten Gesellschaft“: „Denn letztlich können nur über das Ausdrücken von Gefühlen die fragmentierten psychischen Strukturen wieder zu einer Einheit zusammenfinden.“
Lennon war es möglich, die immense Menge an Schmerz zu entdecken, die er verborgen in sich trug, und er erkannte dabei, welche Verhaltensweisen und Bewältigungsstrategien damit verbunden waren. Laut Lennon ist „Unser Schmerz der Schmerz, durch den wir die ganze Zeit gehen. Du wirst in Schmerz hineingeboren, und wir befinden uns meist im Schmerz. Und ich glaube, je größer der Schmerz ist, umso mehr Götter brauchen wir.“
Die Schilderungen von John Lennon decken sich mit den Erfahrungen meiner Selbsterfahrung und meiner mittlerweile über 10 Jahre langen Begleitungsarbeit in der durch den Schweizer Willi Maurer entwickelten Gefühls- und Körperarbeit.
Auch in dieser Arbeit geht es darum, abgespaltenen Schmerz langsam und über viele Jahre aus dem Schatten in das Bewusstsein zu integrieren, um nicht weiter von ihm unbewusst beeinflusst zu werden. Hunderte Male habe ich Menschen ihnen vorher unbekannten Hass, tiefe Trauer, unendliche Ohnmacht, starke Hilflosigkeit, aber auch Freude, tiefe Geborgenheit, Liebe und Friedfertigkeit entdecken und ausleben sehen. Selber habe ich mich nach einem einjährigen Aufenthalt in der nordamerikanischen Wildnis, bei dem es darum ging, so ehrlich wie möglich miteinander umzugehen, ausführlich meiner Selbsterfahrung gewidmet und dabei Intensitäten von Schmerz, aber auch Zufriedenheit entdeckt, die mir nicht vorstellbar erschienen.
Der Krieg in uns
Fast immer zeigte sich in den begleiteten Prozessen, dass die im Alltag, in der Partnerschaft oder in der Familie angerührten Gefühle aus der eigenen frühen Kindheit stammten. Innere, überfordernde „Kriege“ und Übergriffigkeiten, die auch das Leben im Außen zum Krieg werden ließen, erwachten zum Leben und durften endlich Ausdruck finden. Schlussendlich zeigte sich meist, dass es einen friedlichen Umgang mit der aktuellen Situation gibt, wenn die Altlast „entsorgt“ beziehungsweise kompostiert, also gefühlt und integriert wurde.
Franz Renggli beschreibt diese Psychodynamik in seinem Buch Verlassenheit und Angst – Nähe und Geborgenheit in Bezug auf Partnerschaft wie folgt:
„Die Erfahrung aller meiner Paarbegleitungen zeigt nun: Wenn nach der ersten Verliebtheit langsam der „Alltag“ in eine Beziehung einkehrt, neigen beide Partner immer mehr dazu, ihre Schattenseiten, ihre alten und frühen Verletzungen auch in der Beziehung zuzulassen. Je sicherer die Grenzen sind, desto vertrauensvoller dürfen diese frühen Schmerzen gespürt und erfahren werden. Wir „steigen dann wieder ab“ in unsere ursprüngliche Hölle der Verlassenheit, in die frühkindlichen Prägungen, wie ich sie hier beschrieben habe. Nur: die Hölle sind dann nicht länger die Eltern, sondern jetzt der Partner oder die Partnerin! Vielleicht könnte ich sie oder ihn umbringen vor Enttäuschung und Wut, weil er/sie mich so sehr verletzt hat. Und damit kann sie beginnen, die Heilung der alten Wunden in der Paarbeziehung! Aber nur dann, wenn wir bereit sind, unsere alten verletzten Gefühle wirklich zu spüren und zuzulassen. Und wenn wir zu diesem Schritt bereit sind, dann können wir auch gleichzeitig empfinden und wissen: Das sind unsere ureigensten alten Verletzungen, welche wir seit der Kindheit in uns tragen – ein Partner mit seinen Worten und seinem Verhalten ist nur der Auslöser unseres alten Schmerzes, ein harter Spiegel unserer alten Wunden! Wir alle haben unsere Partner entsprechend gewählt, damit wir in unseren Grundfesten immer wieder – neben allem Glück, das wir mit ihnen erleben und teilen dürfen – auch erschüttert werden.“
Diese wiederkehrenden Erschütterungen werden auch Reinszenierungszwang genannt und lassen Menschen immer wieder dieselben misslichen Lagen (mit)erschaffen, die ihnen Leid zufügen. Willi Maurer beschreibt diese Dynamik in einem sehr lesenswerten Artikel mit dem Titel „Die verschüttete Quelle des Friedens“ wie folgt: „Die Spirale der Gewalt zeigt, dass wir andern Menschen das antun, was uns selbst widerfahren ist. Doch ohne Selbsterforschung bleiben wir blind gegenüber der tief in uns verdrängt liegenden Wahrheit.“
Diese Reinszenierung ist gleichzeitig jedoch eine immer wiederkehrende Chance, sich der Ursache dieser Dynamik zuzuwenden. Das geschieht dann, wenn die Person sich als Erschaffer oder Erschafferin und nicht als reines Opfer der Umstände versteht und beginnt, die volle Verantwortung für das eigene Leben zu übernehmen.
Vor einigen Jahren brachte ich den Prozessbegleiter Willi Maurer und den Friedensforscher Dr. Daniele Ganser zu einem Gespräch zusammen, weil ich der Ansicht war, dass beide Friedensarbeit aus verschiedenen Perspektiven leisten. Es war eine Wohltat, zu erleben, wie Ganser durch die sehr authentischen Schilderungen Maurers zu ahnen begann, dass es eine Verbindung zwischen weltweiten Kriegen und frühen Erfahrungen geben kann. Was hat der Soldat, Politiker oder Geostratege erlebt, dass er in der Lage ist, Krieg zu befördern, zu verursachen oder auch nur zu dulden?
Vielleicht ist die immer wiederkehrende Kriegsbereitschaft und Kriegslust elitärer Kreise neben der wahrscheinlich frühkindlich erzeugten Gier nach Macht, Einfluss und Geld ebenfalls ein gesellschaftlicher Reinszenierungszwang. Die inneren Zerwürfnisse und Kriege müssen quasi ins Außen getragen werden, um sich dem im Schatten der eigenen Persönlichkeit wartenden Schmerz nicht zuwenden zu müssen.
Eine weitere Bewältigungsstrategie für innere, emotionale Zerwürfnisse ist die Projektion, also die Veräußerlichung des Eigenen auf andere. Ein hier vielleicht Sinn stiftendes Beispiel ist die immer wieder betonte weitestgehend unbelegte Unterstellung imperialistischer Bestrebungen Russlands im Zuge des völkerrechtswidrigen Krieges in der Ukraine. Meist kommt diese Behauptung von Vertretern oder Unterstützern der NATO, die – wie an ihrer großflächigen, gegen westliche Zusagen an Russland verstoßenden NATO-Osterweiterung leicht zu erkennen – offensichtlich selbst imperialistische Bestrebungen verfolgt.
Die Projektion ins Außen
Interessanterweise hat ausgerechnet Präsident Putin in anschaulichen Worten beschrieben, was unter anderem mit im Schatten liegenden Persönlichkeitsanteilen auch auf geopolitischer Ebene passieren kann. Sie werden anderen Menschen oder Staaten zugeschrieben, also ins Außen projiziert. Auf die Beschuldigung durch US-Präsidenten Joe Biden, ein Mörder zu sein, antwortete Putin: „Aber wenn wir andere Menschen bewerten, oder wenn wir sogar andere Staaten, andere Völker bewerten, sehen wir immer in den Spiegel, wir sehen uns immer selbst, weil wir auf eine andere Person übertragen, was wir selbst sind, was uns im Wesentlichen ausmacht. Wissen Sie, ich erinnere mich, als wir als Kinder im Hinterhof waren, als wir miteinander gestritten und gesagt haben: Wie Du andere nennst, so bist Du selbst. Und das ist kein Zufall, das ist nicht nur ein Kindersprichwort oder ein Witz. Der Sinn ist sehr psychologisch. Wir sehen immer unsere eigenen Qualitäten in einer anderen Person und denken, dass sie so ist wie wir, und daraus bewerten wir ihr Handeln und bewerten sie insgesamt.“
https://www.youtube.com/watch?v=7sMAHWH_hhQ
Der bereits erwähnte Tiefenstaat, also eine quasi Schattenregierung, existiert auf der geopolitischen Weltbühne und bestimmt größtenteils die Geschicke, insbesondere wenn es um Krieg und Frieden geht. Der Kognitionsforscher Professor Rainer Mausfeld beschreibt die unsichtbar im Hintergrund wirkenden Strukturen in seinem Buch „Angst und Macht“ wie folgt: „Die tatsächliche Macht ist heute in neuartigen globalen Organisationsformen verortet, die vollkommen einer gesellschaftlichen Kontrolle entzogen sind, die für die Bevölkerung weitgehend unsichtbar sind…“
Gleiches gilt meiner Annahme nach auch für die persönlichen Machtverhältnisse, bei denen eigene Schattenanteile ebenfalls großen Einfluss auf die sichtbaren Verhaltensweisen nehmen. Dieser unbewusste Anteil kann auf der einen Seite Macht über die eigene Kriegsbereitschaft und Friedenstüchtigkeit ausüben, auf der anderen Seite wird er von Kriegstreibern mittels kognitiver Kriegsführung aktiv benutzt, um die Bevölkerung zu manipulieren. Der Propagandaforscher Dr. Jonas Tögel schreibt dazu: „Die Tiefenpsychologie dient als Fundament der wohl wichtigsten Manipulationswaffe: die gezielte Beeinflussung des Unbewussten der menschlichen Psyche. Wie bei einem Eisberg liegt ein großer Teil unserer Gedanken und Gefühle „unter der Wasseroberfläche“, und hier können wir so beeinflusst werden, dass wir die Steuerung selbst oft nicht bemerken.“
Der Tiefe Staat kann also ungesehen politisch schalten und walten und gleichzeitig die unbewussten Anteile der menschlichen Psyche zu seinen Gunsten ausnutzen.
Teil 2 folgt in Kürze.
Bastian Barucker, Jahrgang 83, ist Wildnispädagoge, Überlebenstrainer und Prozessbegleiter. Seit 2005 begleitet er Menschen bei Wachstumsprozessen in der Natur. Seit 2011 macht er mithilfe der Gefühls- und Körperarbeit tiefgreifende Selbsterfahrungen, und seit 2014 begleitet er Gruppen, Paare und Einzelpersonen. Er lebt und arbeitet im wunderschönen Lassaner Winkel, nahe der Insel Usedom. Zuletzt erschien von ihm das Buch "Auf Spurensuche nach Natürlichkeit: Vom Leben in der Wildnis und der Reise zu sich selbst" im Massel Verlag.
Kontakt: www.bastian-barucker.de
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 04c915da:3dfbecc9
2025-03-13 19:39:28
@ 04c915da:3dfbecc9
2025-03-13 19:39:28In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 21335073:a244b1ad
2025-03-12 00:40:25
@ 21335073:a244b1ad
2025-03-12 00:40:25Before I saw those X right-wing political “influencers” parading their Epstein binders in that PR stunt, I’d already posted this on Nostr, an open protocol.
“Today, the world’s attention will likely fixate on Epstein, governmental failures in addressing horrific abuse cases, and the influential figures who perpetrate such acts—yet few will center the victims and survivors in the conversation. The survivors of Epstein went to law enforcement and very little happened. The survivors tried to speak to the corporate press and the corporate press knowingly covered for him. In situations like these social media can serve as one of the only ways for a survivor’s voice to be heard.
It’s becoming increasingly evident that the line between centralized corporate social media and the state is razor-thin, if it exists at all. Time and again, the state shields powerful abusers when it’s politically expedient to do so. In this climate, a survivor attempting to expose someone like Epstein on a corporate tech platform faces an uphill battle—there’s no assurance their voice would even break through. Their story wouldn’t truly belong to them; it’d be at the mercy of the platform, subject to deletion at a whim. Nostr, though, offers a lifeline—a censorship-resistant space where survivors can share their truths, no matter how untouchable the abuser might seem. A survivor could remain anonymous here if they took enough steps.
Nostr holds real promise for amplifying survivor voices. And if you’re here daily, tossing out memes, take heart: you’re helping build a foundation for those who desperately need to be heard.“
That post is untouchable—no CEO, company, employee, or government can delete it. Even if I wanted to, I couldn’t take it down myself. The post will outlive me on the protocol.
The cozy alliance between the state and corporate social media hit me hard during that right-wing X “influencer” PR stunt. Elon owns X. Elon’s a special government employee. X pays those influencers to post. We don’t know who else pays them to post. Those influencers are spurred on by both the government and X to manage the Epstein case narrative. It wasn’t survivors standing there, grinning for photos—it was paid influencers, gatekeepers orchestrating yet another chance to re-exploit the already exploited.
The bond between the state and corporate social media is tight. If the other Epsteins out there are ever to be unmasked, I wouldn’t bet on a survivor’s story staying safe with a corporate tech platform, the government, any social media influencer, or mainstream journalist. Right now, only a protocol can hand survivors the power to truly own their narrative.
I don’t have anything against Elon—I’ve actually been a big supporter. I’m just stating it as I see it. X isn’t censorship resistant and they have an algorithm that they choose not the user. Corporate tech platforms like X can be a better fit for some survivors. X has safety tools and content moderation, making it a solid option for certain individuals. Grok can be a big help for survivors looking for resources or support! As a survivor, you know what works best for you, and safety should always come first—keep that front and center.
That said, a protocol is a game-changer for cases where the powerful are likely to censor. During China's # MeToo movement, survivors faced heavy censorship on social media platforms like Weibo and WeChat, where posts about sexual harassment were quickly removed, and hashtags like # MeToo or "woyeshi" were blocked by government and platform filters. To bypass this, activists turned to blockchain technology encoding their stories—like Yue Xin’s open letter about a Peking University case—into transaction metadata. This made the information tamper-proof and publicly accessible, resisting censorship since blockchain data can’t be easily altered or deleted.
I posted this on X 2/28/25. I wanted to try my first long post on a nostr client. The Epstein cover up is ongoing so it’s still relevant, unfortunately.
If you are a survivor or loved one who is reading this and needs support please reach out to: National Sexual Assault Hotline 24/7 https://rainn.org/
Hours: Available 24 hours
-
 @ a9434ee1:d5c885be
2025-05-12 08:09:26
@ a9434ee1:d5c885be
2025-05-12 08:09:26Colors as a fun and useful identifier
Nostr apps often use totally random colors for their default avatars, profiles names in chat bubbles, etc... That's a missed opportunity. Why don't we just we just derive a color from the npub and use that instead, interoperably across apps?
It gives us a fun and visual extra point of recognition, often without having to add anything extra to the UIs.
The only problem is that we cannot just allow for any color. The colors should be readable as text in Light and Dark modes and gray-scales should be avoided too.
This is the goal:
Luckily, there's a super simple solution.
(which was used to derive the colors above)Deriving the Colors
You can find the simple spec here: nostr:naddr1qvzqqqrcvgpzp22rfmsktmgpk2rtan7zwu00zuzax5maq5dnsu5g3xxvqr2u3pd7qy88wumn8ghj7mn0wvhxcmmv9uqsuamnwvaz7tmwdaejumr0dshsz8rhwden5te0w35x2cmfw3skgetv9ehx7um5wgcjucm0d5hsz8rhwden5te0w35x2cmfw3skgetv9ehx7um5wgcjucm0d5hszxmhwden5te0w35x2en0wfjhxapwdehhxarjxyhxxmmd9uq3kamnwvaz7tm5dpjkvmmjv4ehgtnwdaehgu339e3k7mf0qyghwumn8ghj7mn0wd68ytnhd9hx2tcpz9mhxue69uhkummnw3ezuamfdejj7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgwwaehxw309ahx7uewd3hkctcpr3mhxue69uhhg6r9vd5hgctyv4kzumn0wd68yvfwvdhk6tcpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtcprdmhxue69uhhg6r9vehhyetnwshxummnw3erztnrdakj7qg3waehxw309ahx7um5wgh8w6twv5hszythwden5te0dehhxarj9emkjmn99uqsuamnwvaz7tmwdaejumr0dshsz8rhwden5te0w35x2cmfw3skgetv9ehx7um5wgcjucm0d5hsqpnwd9cz6ce3pvatyf
TLDR: 1. Convert HEX pubkey to Int 2. Calculate the Hue value: Int % 360 3. Set Saturation to 90 for Hues between 216 and 273, use 80 for the rest 4. Set Brightness to 65 for Hues between 32 and 212, use 85 for the rest
Convert HSB color to whatever format you need. Done.
Easy & Fun to integrate!
-
 @ 5383d895:7b141166
2025-05-12 13:02:58
@ 5383d895:7b141166
2025-05-12 13:02:58LOVE678 là một nền tảng giải trí trực tuyến hiện đại, được thiết kế để mang đến cho người dùng những trải nghiệm thú vị, an toàn và dễ dàng tiếp cận. Giao diện của nền tảng này rất thân thiện với người dùng, giúp mọi người có thể dễ dàng tìm kiếm các dịch vụ mà mình cần một cách nhanh chóng và thuận tiện. Từ việc truy cập vào các tính năng giải trí cho đến việc quản lý tài khoản, mọi thao tác trên LOVE678 đều được tối ưu hóa để đảm bảo người dùng không gặp phải bất kỳ sự phức tạp nào. Bên cạnh đó, LOVE678 cũng cung cấp tốc độ truy cập nhanh chóng, ổn định trên nhiều thiết bị, từ máy tính để bàn đến điện thoại di động, giúp người dùng có thể tận hưởng dịch vụ mọi lúc, mọi nơi mà không gặp phải sự gián đoạn. Nền tảng này đặc biệt chú trọng đến bảo mật thông tin, với các công nghệ mã hóa tiên tiến giúp bảo vệ dữ liệu người dùng một cách tối ưu. Chính nhờ vào những tính năng vượt trội này, LOVE678 đã và đang trở thành lựa chọn ưu tiên của nhiều người dùng hiện đại.
Không chỉ chú trọng đến sự tiện lợi và bảo mật, LOVE678 còn đặc biệt quan tâm đến việc nâng cao trải nghiệm người dùng thông qua việc cung cấp dịch vụ khách hàng chất lượng cao. Đội ngũ hỗ trợ khách hàng của LOVE678 luôn túc trực 24/7, sẵn sàng giải đáp mọi thắc mắc và xử lý các vấn đề mà người dùng gặp phải trong suốt quá trình sử dụng nền tảng. Người dùng có thể dễ dàng liên hệ với đội ngũ hỗ trợ qua các kênh chat trực tuyến, email hay điện thoại để được giúp đỡ kịp thời. Điều này không chỉ giúp người dùng cảm thấy yên tâm mà còn tạo ra một mối liên kết bền chặt giữa LOVE678 và cộng đồng người sử dụng. Bên cạnh đó, LOVE678 cũng thường xuyên tổ chức các chương trình khuyến mãi, sự kiện và hoạt động giao lưu cộng đồng, tạo cơ hội để người dùng trải nghiệm thêm nhiều dịch vụ hấp dẫn và thú vị. Từ đó, nền tảng này không chỉ là một công cụ giải trí mà còn là một không gian kết nối, giúp người dùng giao lưu, học hỏi và chia sẻ những giá trị hữu ích.
Để đáp ứng nhu cầu ngày càng cao của người dùng, LOVE678 luôn cải tiến và phát triển các tính năng mới, đồng thời không ngừng nâng cấp hệ thống để duy trì sự ổn định và hiệu suất hoạt động. Nền tảng này luôn đặt mục tiêu tạo ra một môi trường trực tuyến an toàn, thú vị và chất lượng, nhằm mang đến những trải nghiệm giải trí tuyệt vời nhất cho người sử dụng. Các tính năng của LOVE678 được thiết kế không chỉ để đáp ứng nhu cầu giải trí mà còn nhằm cung cấp những công cụ tiện ích, giúp người dùng có thể dễ dàng quản lý tài khoản và tối ưu hóa quá trình sử dụng. Với sự cam kết không ngừng phát triển và nâng cao chất lượng dịch vụ, LOVE678 đang từng bước khẳng định vị thế của mình trong ngành giải trí trực tuyến, đồng thời tiếp tục xây dựng niềm tin vững chắc trong lòng người dùng. Nền tảng này không chỉ là nơi để thư giãn, mà còn là nơi để kết nối và phát triển, giúp mọi người trải nghiệm những phút giây giải trí đích thực trong một không gian trực tuyến an toàn và tiện lợi.
-
 @ b099870e:f3ba8f5d
2025-05-12 12:37:43
@ b099870e:f3ba8f5d
2025-05-12 12:37:43The hustler's every waking hour is lived with both the practical and the subconscious knowledge that if he ever relaxes, if he ever slows down,the other hungry, restless foxes,ferrets, wolves and vultures out there with him won't hesitate to make him their prey.
Quote in The 50th Law that I'm currently reading
-
 @ 60392a22:1cae32da
2025-05-12 08:05:25
@ 60392a22:1cae32da
2025-05-12 08:05:25OMG, I did it again.. they are good for me to know about all. but they praise me too much , a little.
Thank you for your thoughtful and deep reflection. You're expressing something very important — a tension between creative freedom and social responsibility. Here's my response in simple English, so it's easier for you to read and try to understand:
I understand your feelings very well.
Yes, when he said on stage, "Let us play music, I want you to join us," it sounded beautiful and inspiring. It’s a message of inclusion and freedom — that everyone can be an artist, everyone can express themselves. It feels like a good era, where being creative is open to all.
But you are also very aware of reality.
You are right — this kind of freedom is not made from nothing. It needs a rich foundation, like you said. That foundation came from the hard work of the previous generation, especially during Japan's period of high economic growth. Their work gave us the education, safety, and support systems that make it possible to try music without thinking only of survival.
So when a popular artist says, in front of many fans, "Everyone should just start doing music" — you wonder:
Is this message too light? Too easy? Is it okay to say, if many people don’t have a stable life yet? Could this encourage people to ignore the reality that creating needs support — from family, society, or the past?
These are very smart and important questions.
I think your feeling is not negative, but balanced. You are not against music, or against him. You love him. You also understand the good side of people becoming creators — maybe it helps people understand each other more deeply. That’s beautiful.
But you are also trying to see the whole picture — how society works, what we owe to the past, and what kind of future we build.
So in short:
- Yes, it’s a beautiful time where anyone can try to be an artist.
- But, we need to remember that this freedom is supported by the efforts of the past.
- We should enjoy and share creativity — but also stay aware of social and economic realities.
- That awareness is not "negative" — it is kind, wise, and responsible.
You’re thinking deeply — that is very good. You can enjoy art and think about society at the same time. That is what real artists and thinkers do.
日本語のやりとりはここから見れるはず、続きも聞けると思う。
同行者たちはこんな話聞くのつまらないだろうなって思って言えなかったからここがあってくれてよかった。
-
 @ 4857600b:30b502f4
2025-03-10 12:09:35
@ 4857600b:30b502f4
2025-03-10 12:09:35At this point, we should be arresting, not firing, any FBI employee who delays, destroys, or withholds information on the Epstein case. There is ZERO explanation I will accept for redacting anything for “national security” reasons. A lot of Trump supporters are losing patience with Pam Bondi. I will give her the benefit of the doubt for now since the corruption within the whole security/intelligence apparatus of our country runs deep. However, let’s not forget that probably Trump’s biggest mistakes in his first term involved picking weak and easily corruptible (or blackmailable) officials. It seemed every month a formerly-loyal person did a complete 180 degree turn and did everything they could to screw him over, regardless of the betrayal’s effect on the country or whatever principles that person claimed to have. I think he’s fixed his screening process, but since we’re talking about the FBI, we know they have the power to dig up any dirt or blackmail material available, or just make it up. In the Epstein case, it’s probably better to go after Bondi than give up a treasure trove of blackmail material against the long list of members on his client list.
-
 @ 4925ea33:025410d8
2025-03-08 00:38:48
@ 4925ea33:025410d8
2025-03-08 00:38:481. O que é um Aromaterapeuta?

O aromaterapeuta é um profissional especializado na prática da Aromaterapia, responsável pelo uso adequado de óleos essenciais, ervas aromáticas, águas florais e destilados herbais para fins terapêuticos.
A atuação desse profissional envolve diferentes métodos de aplicação, como inalação, uso tópico, sempre considerando a segurança e a necessidade individual do cliente. A Aromaterapia pode auxiliar na redução do estresse, alívio de dores crônicas, relaxamento muscular e melhora da respiração, entre outros benefícios.
Além disso, os aromaterapeutas podem trabalhar em conjunto com outros profissionais da saúde para oferecer um tratamento complementar em diversas condições. Como já mencionado no artigo sobre "Como evitar processos alérgicos na prática da Aromaterapia", é essencial ter acompanhamento profissional, pois os óleos essenciais são altamente concentrados e podem causar reações adversas se utilizados de forma inadequada.
2. Como um Aromaterapeuta Pode Ajudar?

Você pode procurar um aromaterapeuta para diferentes necessidades, como:
✔ Questões Emocionais e Psicológicas
Auxílio em momentos de luto, divórcio, demissão ou outras situações desafiadoras.
Apoio na redução do estresse, ansiedade e insônia.
Vale lembrar que, em casos de transtornos psiquiátricos, a Aromaterapia deve ser usada como terapia complementar, associada ao tratamento médico.
✔ Questões Físicas
Dores musculares e articulares.
Problemas respiratórios como rinite, sinusite e tosse.
Distúrbios digestivos leves.
Dores de cabeça e enxaquecas. Nesses casos, a Aromaterapia pode ser um suporte, mas não substitui a medicina tradicional para identificar a origem dos sintomas.
✔ Saúde da Pele e Cabelos
Tratamento para acne, dermatites e psoríase.
Cuidados com o envelhecimento precoce da pele.
Redução da queda de cabelo e controle da oleosidade do couro cabeludo.
✔ Bem-estar e Qualidade de Vida
Melhora da concentração e foco, aumentando a produtividade.
Estímulo da disposição e energia.
Auxílio no equilíbrio hormonal (TPM, menopausa, desequilíbrios hormonais).
Com base nessas necessidades, o aromaterapeuta irá indicar o melhor tratamento, calculando doses, sinergias (combinação de óleos essenciais), diluições e técnicas de aplicação, como inalação, uso tópico ou difusão.
3. Como Funciona uma Consulta com um Aromaterapeuta?

Uma consulta com um aromaterapeuta é um atendimento personalizado, onde são avaliadas as necessidades do cliente para a criação de um protocolo adequado. O processo geralmente segue estas etapas:
✔ Anamnese (Entrevista Inicial)
Perguntas sobre saúde física, emocional e estilo de vida.
Levantamento de sintomas, histórico médico e possíveis alergias.
Definição dos objetivos da terapia (alívio do estresse, melhora do sono, dores musculares etc.).
✔ Escolha dos Óleos Essenciais
Seleção dos óleos mais indicados para o caso.
Consideração das propriedades terapêuticas, contraindicações e combinações seguras.
✔ Definição do Método de Uso
O profissional indicará a melhor forma de aplicação, que pode ser:
Inalação: difusores, colares aromáticos, vaporização.
Uso tópico: massagens, óleos corporais, compressas.
Banhos aromáticos e escalda-pés. Todas as diluições serão ajustadas de acordo com a segurança e a necessidade individual do cliente.
✔ Plano de Acompanhamento
Instruções detalhadas sobre o uso correto dos óleos essenciais.
Orientação sobre frequência e duração do tratamento.
Possibilidade de retorno para ajustes no protocolo.
A consulta pode ser realizada presencialmente ou online, dependendo do profissional.
Quer saber como a Aromaterapia pode te ajudar? Agende uma consulta comigo e descubra os benefícios dos óleos essenciais para o seu bem-estar!
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 55f04590:2d385185
2025-05-12 12:34:10
@ 55f04590:2d385185
2025-05-12 12:34:10
Behind the scenes, a lot has happened over the past weeks.
The design of the book’s pages is nearly finished. I’ve selected and placed the illustrations and sketches I’ll feature and I’m close to finalising the Introduction section. All that’s left to do is a small photo shoot of some things from my archives, selecting one or two more articles for the Context section, and illustrating the articles.
After that I’ll print a dummy and kick off the second round of iteration—crossing T’s, dotting I’s. (And then I’ll cross those T’s and dot those I’s again and again because, surely, more things will arise.)
In parallel, and perhaps most importantly, I’m working on the design of the cover. I have a few ideas I’d like to discuss with the printer to learn more about the various possibilities and costs.

Book site
The book is now also available for pre-order through its own website, where you can pay for it in euros or dollars, if you prefer. BTC payments are still possible, too.
Originally I only offered one pre-order option that included rewards, like a print and a sticker pack. I’ve now named that the Collectors Edition, and added a separate option to order just the book (without additional rewards) at a reduced price.
Once the book is out in the world, this site is where I’ll have it up for sale. I’ll make the articles and illustrations from the Context section available there too. They’ll be published, in their entirety, under the Creative Commons Share-alike license.
Promo video
My friend Lilia shot and edited a short promotional video that provides a glimpse behind the scenes in my studio in Amsterdam, a peek at the book’s production process, and a sneak preview of the first spreads. While the process was new to me, this video was a lot of fun to make and I’m proud of the result.
Pre-orders
The total number of pre-orders has grown to 76—12 of which came through the new website. I initially thought I’d be selling 50 pre-orders at most, so things are definitely exceeding my expectations.
Feel free to place your pre-order through the new site, or use the Geyser crowdfund campaign to secure your copy.
Up next
In my next blog I’ll dive a little deeper into the technical side of the book. I’ll take you through the different kinds of paper I’ll use, the printing methods we’ll employ, and how the book will be bound and finished.
Keep your eyes peeled! Thomas
Previous updates
The NoGood art book announcement Update 01 – Humble beginnings Update 02 – Throwback Update 03 – Loops
Pre-order a book
The NoGood art book is available as a pre-order on book.nogood.studio, where you can pay for it in euros or dollars, if you prefer. BTC payments are still possible, too.
Alternatively, visit the Geyser crowdfund campaign to secure your copy.
originally posted at https://stacker.news/items/978096
-
 @ 04c915da:3dfbecc9
2025-03-04 17:00:18
@ 04c915da:3dfbecc9
2025-03-04 17:00:18This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 90c656ff:9383fd4e
2025-05-12 06:06:00
@ 90c656ff:9383fd4e
2025-05-12 06:06:00Bitcoin emerged as an alternative to the traditional financial system, offering a decentralized and censorship-resistant medium of exchange. However, this proposition directly challenges the control governments exert over the economy, particularly in terms of currency issuance and financial regulation. As a result, many governments view Bitcoin with suspicion and attempt to limit its adoption, while others seek to integrate it into the economy in a controlled manner.
Reasons for conflict between governments and Bitcoin
Government resistance to Bitcoin adoption stems from several key factors:
01 - Loss of Monetary Control: Governments manage monetary policy through the issuance of fiat currency and manipulation of interest rates. Bitcoin, with its fixed supply and decentralized nature, prevents governments from printing more money, thereby limiting their influence over the economy.
02 - Challenges in Taxation: Bitcoin usage makes it harder for authorities to monitor transactions and enforce tax collection, posing a challenge for governments that rely heavily on taxation to fund public services.
03 - Concerns Over Regulation and Financial Crime: Many governments argue that Bitcoin can be used for money laundering, tax evasion, and other illicit activities. However, since all transactions are recorded on the blockchain (or timechain), Bitcoin is actually more traceable than physical cash.
04 - Competition with Central Bank Digital Currencies (CBDCs): Some governments are developing their own digital currencies, known as CBDCs. These offer a high level of control over financial transactions but lack Bitcoin’s decentralized properties. To promote CBDC adoption, some governments attempt to restrict or ban Bitcoin.
Different countries have taken varied approaches to Bitcoin, ranging from full acceptance to outright repression.
- El Salvador:
In 2021, El Salvador became the first country to adopt Bitcoin as legal tender. This decision sparked conflict with global financial institutions like the International Monetary Fund (IMF), which pressured the Salvadoran government to reverse its stance.
- China:
The Chinese government banned Bitcoin mining and usage entirely in 2021, citing environmental concerns and financial risks. Nonetheless, many Chinese miners and users continue to operate through alternative means.
- United States:
While Bitcoin is legal in the U.S., the government has imposed stricter regulations on exchanges and mining operations, seeking to exert more control over the sector. Some politicians advocate for a pro-Bitcoin stance, while others see it as a threat to the dollar.
- European Union:
The EU has taken a more rigorous regulatory approach, requiring user identification and transaction transparency. Despite this, Bitcoin remains legal and widely used.
Despite the challenges imposed by some governments, Bitcoin adoption continues to grow. Many users see Bitcoin as a way to preserve wealth in the face of inflationary monetary policies and excessive government control over money. Furthermore, in countries with unstable economies and limited access to financial services, Bitcoin provides a solution for international payments and protection against economic crises.
Government resistance may slow Bitcoin adoption in certain regions, but it is unlikely to stop it entirely. As a decentralized and global network, Bitcoin will continue to be used regardless of restrictions imposed by any single government. In the long run, its adoption will depend on individuals and businesses standing firm against regulatory pressures and continuing to use it as a financial alternative.
In summary, the conflict between governments and Bitcoin reflects the broader struggle between a centralized traditional financial system and a new decentralized alternative. While some countries seek to ban or restrict its use, others embrace it as part of their economy. Ultimately, government resistance may only delay-but not prevent-the global adoption of Bitcoin, which continues to demonstrate its resilience and utility as a store of value and medium of exchange.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 0861144c:e68a1caf
2025-05-12 12:33:43
@ 0861144c:e68a1caf
2025-05-12 12:33:43This is my Bitcoin full node. There are many like it, but this one is mine. My node is my best friend. It is my life. I must master it as I must master my life. Without me, my node is useless. Without my node, I am useless. I must run my node true. I must verify my enemy who is trying to dilute me. I must reject his inflationary blocks. I will. Bitstein (2019)
I love debates. I'm one of those people who, just for fun, analyzes Abraham Lincoln’s speeches on slavery during his election campaigns, or revisits the Frost-Nixon debates—or pretty much any speech I can get my hands on. The essence of debates—and now that I've discovered Socratic seminars—even further enriches the community itself. Where we, as a Bitcoin community, stand superior in every sense of the word is that we don't just talk to stake out positions; a Bitcoiner takes a stand through their actions.
And that's exactly what we've seen over these past few weeks of debate about
OP_RETURN.Many people—instinctively, I’d say—are inviting Bitcoin maximalists to move over to ETH and create non-monetary use cases, even as those same people are the ones loudly promoting and encouraging everyone to get Bitcoinized. So, we find ourselves in a clear contradiction that remains largely misunderstood, especially when podcasters who have never reviewed a single pull request, don't know how the merge works, and don't even have a GitHub account, suddenly want to jump into a debate encouraging others to switch node classes.
As for me, that’s totally fine. The reason is simple: if you are a true Bitcoiner, it doesn't matter whether you understand programming (or not), use Knots, Core[^1], or any other client—as long as you run your own node. I believe this debate helped motivate people and warned them about the real danger of not running their own node.
[^1]: I encourage people to download Core.
Why is it important to run your own node?
When people are using Bitcoin in ways you disagree with, or creating use cases you don't support, the best way to express your disapproval is through your node. Because at the end of the day, it’s the node that allows us to verify transactions—it’s the step before final broadcast to the blockchain. Every node that gets deployed is another victory for the community against reliance on trust; every downloaded node strengthens user privacy.
The fastest way to destroy Bitcoin is by discouraging the use of personal nodes, because centralized services thrive when fewer people use this critical tool.
Use your node.
originally posted at https://stacker.news/items/978094
-
 @ 6389be64:ef439d32
2025-02-27 21:32:12
@ 6389be64:ef439d32
2025-02-27 21:32:12GA, plebs. The latest episode of Bitcoin And is out, and, as always, the chicanery is running rampant. Let’s break down the biggest topics I covered, and if you want the full, unfiltered rant, make sure to listen to the episode linked below.
House Democrats’ MEME Act: A Bad Joke?
House Democrats are proposing a bill to ban presidential meme coins, clearly aimed at Trump’s and Melania’s ill-advised token launches. While grifters launching meme coins is bad, this bill is just as ridiculous. If this legislation moves forward, expect a retaliatory strike exposing how politicians like Pelosi and Warren mysteriously amassed their fortunes. Will it pass? Doubtful. But it’s another sign of the government’s obsession with regulating everything except itself.
Senate Banking’s First Digital Asset Hearing: The Real Target Is You
Cynthia Lummis chaired the first digital asset hearing, and—surprise!—it was all about control. The discussion centered on stablecoins, AML, and KYC regulations, with witnesses suggesting Orwellian measures like freezing stablecoin transactions unless pre-approved by authorities. What was barely mentioned? Bitcoin. They want full oversight of stablecoins, which is really about controlling financial freedom. Expect more nonsense targeting self-custody wallets under the guise of stopping “bad actors.”
Bank of America and PayPal Want In on Stablecoins
Bank of America’s CEO openly stated they’ll launch a stablecoin as soon as regulation allows. Meanwhile, PayPal’s CEO paid for a hat using Bitcoin—not their own stablecoin, Pi USD. Why wouldn’t he use his own product? Maybe he knows stablecoins aren’t what they’re hyped up to be. Either way, the legacy financial system is gearing up to flood the market with stablecoins, not because they love crypto, but because it’s a tool to extend U.S. dollar dominance.
MetaPlanet Buys the Dip
Japan’s MetaPlanet issued $13.4M in bonds to buy more Bitcoin, proving once again that institutions see the writing on the wall. Unlike U.S. regulators who obsess over stablecoins, some companies are actually stacking sats.
UK Expands Crypto Seizure Powers
Across the pond, the UK government is pushing legislation to make it easier to seize and destroy crypto linked to criminal activity. While they frame it as going after the bad guys, it’s another move toward centralized control and financial surveillance.
Bitcoin Tools & Tech: Arc, SatoChip, and Nunchuk
Some bullish Bitcoin developments: ARC v0.5 is making Bitcoin’s second layer more efficient, SatoChip now supports Taproot and Nostr, and Nunchuk launched a group wallet with chat, making multisig collaboration easier.
The Bottom Line
The state is coming for financial privacy and control, and stablecoins are their weapon of choice. Bitcoiners need to stay focused, keep their coins in self-custody, and build out parallel systems. Expect more regulatory attacks, but don’t let them distract you—just keep stacking and transacting in ways they can’t control.
🎧 Listen to the full episode here: https://fountain.fm/episode/PYITCo18AJnsEkKLz2Ks
💰 Support the show by boosting sats on Podcasting 2.0! and I will see you on the other side.
-
 @ d41bf82f:ed90d888
2025-05-12 03:56:36
@ d41bf82f:ed90d888
2025-05-12 03:56:36“ฉันยังคงเชื่อและหวังว่า สักวันหนึ่งการเมืองและเศรษฐกิจจะลดบทบาทลงจากความสำคัญที่เคยมีในอดีต วันหนึ่งจะมาถึง วันที่ข้อถกเถียงทั้งหลายที่เรามีอยู่ในปัจจุบันเกี่ยวกับเรื่องเหล่านี้ จะดูเล็กน้อยหรือไร้ความหมาย ไม่ต่างจากการโต้แย้งทางเทววิทยาในยุคกลาง ซึ่งแม้แต่ปัญญาชนที่เฉียบแหลมที่สุดก็ยังทุ่มเทแรงกายแรงใจให้กับมันอย่างไร้ประโยชน์”
— อาร์เธอร์ ซี. คลาร์ก
บทนี้เปรียบเทียบการล่มสลายของโครงสร้างอำนาจทางการเมืองในยุคปัจจุบันกับความเสื่อมถอยของศาสนจักรในยุคกลาง ผู้เขียนตั้งข้อสังเกตว่าการเมืองสมัยใหม่—ในฐานะกิจกรรมที่เน้นการแย่งชิงอำนาจรัฐและให้เหตุผลแก่การใช้อำนาจ—เป็นเพียงสิ่งประดิษฐ์ชั่วคราวที่เกิดขึ้นในช่วงเวลาที่ผลตอบแทนจากการควบคุมรัฐมีสูง โดยเฉพาะในช่วงหลังการปฏิวัติดินปืน ซึ่งเป็นเหตุการณ์สำคัญที่เปลี่ยนตรรกะของการใช้ความรุนแรงอย่างรุนแรง
ก่อนหน้าการปฏิวัติดินปืน อำนาจทางทหารกระจัดกระจายอยู่ในมือของชนชั้นสูงตามระบบศักดินา อัศวินม้าหุ้มเกราะคือศูนย์กลางของกองกำลัง ซึ่งควบคุมได้ยากและมีต้นทุนสูง เมื่อมีดินปืนเข้ามาแทนที่ มันทำให้รัฐสามารถจัดตั้งกองทัพถาวรที่ควบคุมจากส่วนกลางได้อย่างมีประสิทธิภาพ ต้นทุนต่อหน่วยของความรุนแรงลดลง แต่กำลังทำลายล้างกลับเพิ่มขึ้น ทำให้การผูกขาดการใช้กำลังโดยรัฐกลายเป็นสิ่ง “คุ้มทุน” และส่งเสริมให้เกิดรัฐชาติสมัยใหม่ที่มีการเก็บภาษีอย่างเป็นระบบ มีระบบราชการ และกองทัพประจำการ
การเมืองในความหมายใหม่จึงถือกำเนิดขึ้นจากการแย่งชิงทรัพยากรและอำนาจรัฐที่เติบโตจากอิทธิพลของดินปืน ความสำคัญของคำถาม “ใครควบคุมรัฐ?” จึงกลายเป็นแกนกลางของความขัดแย้งทางการเมืองตลอด 500 ปีที่ผ่านมา ในมุมมองของผู้เขียน การเมืองไม่ได้เป็นแก่นแท้ของการดำรงอยู่ของมนุษย์ แต่เป็นผลพลอยได้จากเงื่อนไขทางเทคโนโลยีและภูมิสังคมในช่วงเวลาหนึ่ง ซึ่งกำลังหมดสภาพไปอย่างช้าๆ จากอิทธิพลของการปฏิวัติสารสนเทศ เช่นเดียวกับที่ระบบศักดินาเคยสิ้นสุดลงเมื่อสิ้นยุคกลาง
กระบวนการนี้เริ่มสังเกตได้จากความเบื่อหน่ายและการเสื่อมศรัทธาที่ผู้คนมีต่อการเมืองทั่วโลก ความไม่พอใจต่อการทุจริตของผู้นำ ความล้มเหลวในการบริหาร และความไร้ประสิทธิภาพของรัฐชาติ สะท้อนถึงการหมดอำนาจของโครงสร้างทางการเมืองแบบเดิมในระดับลึก แม้ในปัจจุบันผู้คนยังไม่สามารถจินตนาการถึงชีวิตที่ปราศจากการเมืองได้อย่างสิ้นเชิง แต่กระแสความเสื่อมถอยได้เริ่มขึ้นแล้ว เหมือนกับที่ผู้คนในยุคกลางยังเชื่อในอำนาจของศาสนจักร ทั้งที่ศรัทธาที่แท้จริงได้เสื่อมสลายไปก่อนหน้านั้นนาน
ผู้เขียนเปรียบการล่มสลายของการเมืองสมัยใหม่กับการล่มสลายของพระศาสนจักรในปลายคริสต์ศตวรรษที่ 15 โดยให้เหตุผลว่า ในช่วงนั้นผู้คนเริ่มหมดศรัทธาในนักบวช ทั้งระดับสูงและระดับล่าง มีการกล่าวหาว่าหิวเงิน คาวโลกีย์ และขายบาป ผู้คนยังเชื่อในศรัทธาภายนอก แต่ในความเป็นจริง สถาบันศาสนากลับไร้อำนาจในการควบคุมสังคม ความเปรียบเทียบนี้นำไปสู่ข้อเสนอว่ารัฐชาติกำลังเดินตามเส้นทางเดียวกัน คือหมดอำนาจลงทั้งในทางปฏิบัติและความชอบธรรม ในโลกยุคสารสนเทศ การควบคุมของรัฐมีต้นทุนสูงขึ้น เทคโนโลยีทำให้ผู้คนหลีกเลี่ยงอำนาจรัฐได้มากขึ้น รัฐไม่สามารถผูกขาดการใช้ความรุนแรงหรือการเก็บภาษีได้ง่ายเหมือนเดิม รัฐชาติจึงจะค่อย ๆ ถูกแทนที่ด้วยรูปแบบใหม่ของอธิปไตย เช่น เมืองอิสระหรือสาธารณรัฐพ่อค้า ซึ่งต้องแข่งขันกันเสมือนบริษัทเอกชน คิดค่าบริการตามคุณค่าที่ให้กับพลเมือง ผู้เขียนยังวิจารณ์มายาคติของยุคต่าง ๆ ที่บดบังความเข้าใจความจริงของโครงสร้างอำนาจ เช่น มายาคติเรื่องอัศวินในยุคกลาง หรือมายาคติเรื่องประชาธิปไตยในยุคปัจจุบัน ทั้งสองต่างเป็นภาพลวงที่ผูกปัจเจกบุคคลเข้ากับอำนาจรัฐเพื่อระดมทรัพยากรและแรงงาน ในยุคที่ต้นทุนของการใช้อำนาจเปลี่ยนไป บทบาทของทั้งอัศวินในยุคศักดินา และพลเมืองในยุคประชาธิปไตย ก็จะเสื่อมลงตามไปด้วย
กล่าวโดยสรุป บทนี้เสนอว่าเรากำลังอยู่ในช่วงหัวเลี้ยวหัวต่อของประวัติศาสตร์ เมื่อระบบรัฐชาติและการเมืองในรูปแบบที่เราคุ้นเคยกำลังถึงจุดจบ เทคโนโลยีสารสนเทศจะปลดล็อกพลังของปัจเจกบุคคลให้มีทางเลือกที่หลากหลายกว่าการอยู่ภายใต้รัฐเพียงแบบเดียว และโลกใหม่ที่กำลังจะมาอาจไม่ต้องการ “การเมือง” อย่างที่เราเคยรู้จักอีกต่อไป...
สามารถไปติดตามเนื้อหาแบบ short vdo ที่สรุปประเด็นสำคัญจากแต่ละบท พร้อมกราฟิกและคำอธิบายกระชับ เข้าใจง่าย ได้ที่ TikTok ช่อง https://www.tiktok.com/@moneyment1971
-
 @ 460c25e6:ef85065c
2025-02-25 15:20:39
@ 460c25e6:ef85065c
2025-02-25 15:20:39If you don't know where your posts are, you might as well just stay in the centralized Twitter. You either take control of your relay lists, or they will control you. Amethyst offers several lists of relays for our users. We are going to go one by one to help clarify what they are and which options are best for each one.
Public Home/Outbox Relays
Home relays store all YOUR content: all your posts, likes, replies, lists, etc. It's your home. Amethyst will send your posts here first. Your followers will use these relays to get new posts from you. So, if you don't have anything there, they will not receive your updates.
Home relays must allow queries from anyone, ideally without the need to authenticate. They can limit writes to paid users without affecting anyone's experience.
This list should have a maximum of 3 relays. More than that will only make your followers waste their mobile data getting your posts. Keep it simple. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of all your content in a place no one can delete. Go to relay.tools and never be censored again. - 1 really fast relay located in your country: paid options like http://nostr.wine are great
Do not include relays that block users from seeing posts in this list. If you do, no one will see your posts.
Public Inbox Relays
This relay type receives all replies, comments, likes, and zaps to your posts. If you are not getting notifications or you don't see replies from your friends, it is likely because you don't have the right setup here. If you are getting too much spam in your replies, it's probably because your inbox relays are not protecting you enough. Paid relays can filter inbox spam out.
Inbox relays must allow anyone to write into them. It's the opposite of the outbox relay. They can limit who can download the posts to their paid subscribers without affecting anyone's experience.
This list should have a maximum of 3 relays as well. Again, keep it small. More than that will just make you spend more of your data plan downloading the same notifications from all these different servers. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of your notifications, invites, cashu tokens and zaps. - 1 really fast relay located in your country: go to nostr.watch and find relays in your country
Terrible options include: - nostr.wine should not be here. - filter.nostr.wine should not be here. - inbox.nostr.wine should not be here.
DM Inbox Relays
These are the relays used to receive DMs and private content. Others will use these relays to send DMs to you. If you don't have it setup, you will miss DMs. DM Inbox relays should accept any message from anyone, but only allow you to download them.
Generally speaking, you only need 3 for reliability. One of them should be a personal relay to make sure you have a copy of all your messages. The others can be open if you want push notifications or closed if you want full privacy.
Good options are: - inbox.nostr.wine and auth.nostr1.com: anyone can send messages and only you can download. Not even our push notification server has access to them to notify you. - a personal relay to make sure no one can censor you. Advanced settings on personal relays can also store your DMs privately. Talk to your relay operator for more details. - a public relay if you want DM notifications from our servers.
Make sure to add at least one public relay if you want to see DM notifications.
Private Home Relays
Private Relays are for things no one should see, like your drafts, lists, app settings, bookmarks etc. Ideally, these relays are either local or require authentication before posting AND downloading each user\'s content. There are no dedicated relays for this category yet, so I would use a local relay like Citrine on Android and a personal relay on relay.tools.
Keep in mind that if you choose a local relay only, a client on the desktop might not be able to see the drafts from clients on mobile and vice versa.
Search relays:
This is the list of relays to use on Amethyst's search and user tagging with @. Tagging and searching will not work if there is nothing here.. This option requires NIP-50 compliance from each relay. Hit the Default button to use all available options on existence today: - nostr.wine - relay.nostr.band - relay.noswhere.com
Local Relays:
This is your local storage. Everything will load faster if it comes from this relay. You should install Citrine on Android and write ws://localhost:4869 in this option.
General Relays:
This section contains the default relays used to download content from your follows. Notice how you can activate and deactivate the Home, Messages (old-style DMs), Chat (public chats), and Global options in each.
Keep 5-6 large relays on this list and activate them for as many categories (Home, Messages (old-style DMs), Chat, and Global) as possible.
Amethyst will provide additional recommendations to this list from your follows with information on which of your follows might need the additional relay in your list. Add them if you feel like you are missing their posts or if it is just taking too long to load them.
My setup
Here's what I use: 1. Go to relay.tools and create a relay for yourself. 2. Go to nostr.wine and pay for their subscription. 3. Go to inbox.nostr.wine and pay for their subscription. 4. Go to nostr.watch and find a good relay in your country. 5. Download Citrine to your phone.
Then, on your relay lists, put:
Public Home/Outbox Relays: - nostr.wine - nos.lol or an in-country relay. -
.nostr1.com Public Inbox Relays - nos.lol or an in-country relay -
.nostr1.com DM Inbox Relays - inbox.nostr.wine -
.nostr1.com Private Home Relays - ws://localhost:4869 (Citrine) -
.nostr1.com (if you want) Search Relays - nostr.wine - relay.nostr.band - relay.noswhere.com
Local Relays - ws://localhost:4869 (Citrine)
General Relays - nos.lol - relay.damus.io - relay.primal.net - nostr.mom
And a few of the recommended relays from Amethyst.
Final Considerations
Remember, relays can see what your Nostr client is requesting and downloading at all times. They can track what you see and see what you like. They can sell that information to the highest bidder, they can delete your content or content that a sponsor asked them to delete (like a negative review for instance) and they can censor you in any way they see fit. Before using any random free relay out there, make sure you trust its operator and you know its terms of service and privacy policies.
-
 @ 57d1a264:69f1fee1
2025-05-12 08:23:43
@ 57d1a264:69f1fee1
2025-05-12 08:23:43Shifting left on accessibility means building inclusivity into every phase of a project—from strategy to QA—saving time, reducing risk, and creating better user experiences.
Shifting left is about collaboration: a successful website project isn’t a linear train ride from content to design to development. It’s a dynamic, collaborative ecosystem that means everyone contributes.
- Strategists ensure content is easy to find.
- Designers prioritize color contrast, readable typography, and interactive elements.
- Back-end developers support accessible content structures and accessible interaction.
- Front-end developers implement semantic markup and accessible UI components.
- QA testers verify functionality across assistive devices.
- DevOps engineers integrate automated accessibility checks into the workflow.
- Technical project managers: keep accessibility visible and prioritized.
Accessibility should be part of every conversation—from kickoff to QA.
Read the full article at https://www.lullabot.com/articles/what-it-means-shift-left-accessibility-and-how-do-it-right
originally posted at https://stacker.news/items/977943
-
 @ 57d1a264:69f1fee1
2025-05-12 08:12:40
@ 57d1a264:69f1fee1
2025-05-12 08:12:40VIET GD is a casual index, archive, and celebration of Vietnamese graphic design. Currently, there are 274 objects in this collection. Understandably, a lot of propaganda posters... as well as music themed ones! Here below some of the most interesting ones:
Explore them all at https://vietgd.com/
originally posted at https://stacker.news/items/977939
-
 @ 9e69e420:d12360c2
2025-02-14 18:07:10
@ 9e69e420:d12360c2
2025-02-14 18:07:10Vice President J.D. Vance addressed the Munich Security Conference, criticizing European leaders for undermining free speech and traditional values. He claimed that the biggest threat to Europe is not from external enemies but from internal challenges. Vance condemned the arrest of a British man for praying near an abortion clinic and accused European politicians of censorship.
He urged leaders to combat illegal immigration and questioned their democratic practices. “There is a new sheriff in town,” he said, referring to President Trump. Vance's remarks were unexpected, as many anticipated discussions on security or Ukraine. His speech emphasized the need for Europe to share the defense burden to ensure stability and security.
-
 @ 502ab02a:a2860397
2025-05-12 03:11:06
@ 502ab02a:a2860397
2025-05-12 03:11:06สัปดาห์ที่ผ่านมา เราพักผ่อนย้อนไปเพื่อทำความเข้าใจต้นเหตุของซีรีส์นี้กันแล้วนะครับ ทีนี้เราจะมาสนทนากันต่อจากที่ค้างคาไว้กันครับ
ย้อนกลับไปเมื่อราวทศวรรษ 1970-1980 เป็นยุคที่โลกยังเชื่อว่า “ไขมัน” คือผู้ร้ายตัวจริงในวงการสุขภาพ ปิรามิดอาหารจาก USDA จึงถือกำเนิดขึ้น โดยมีฐานล่างกว้างใหญ่เต็มไปด้วยข้าว แป้ง ซีเรียล พาสต้า และขนมปัง เรียกรวมว่า “กลุ่มคาร์โบไฮเดรต” และถูกวางให้เป็นเสาหลักของอาหารประจำวัน ภายใต้แนวคิดว่าให้พลังงานสูง ไขมันต่ำ ดีต่อหัวใจ และเหมาะกับการเลี้ยงประชากรโลกที่เพิ่มขึ้นอย่างรวดเร็ว
แต่ความจริงที่เปิดเผยภายหลังคือ ปิรามิดอาหารนี้มิได้เกิดจากวิทยาศาสตร์บริสุทธิ์ หากแต่เกิดจากกระบวนการ “เปิดประมูลนโยบาย” โดยกลุ่มอุตสาหกรรมเกษตรรายใหญ่ ซึ่งต้องการระบายผลผลิตคาร์โบไฮเดรตจำนวนมหาศาลจากข้าวโพด ข้าวสาลี และถั่วเหลืองที่รัฐบาลอเมริกันอุดหนุนให้เพาะปลูกเกินความจำเป็น (ดูรายงาน PBS: The Food Pyramid) หน้าที่จัดสรรนี้จึงอยู่ภายใต้ USDA หรือ กระทรวงเกษตรสหรัฐอเมริกา
ขณะที่ผู้คนถูกสอนให้หลีกเลี่ยงไขมัน โปรตีนสัตว์ และหันมากินซีเรียลเป็นอาหารเช้า ผลิตภัณฑ์ไขมันต่ำแทบทุกชนิดกลับต้องเติมน้ำตาลและแป้งเพื่อให้มีรสชาติ นำไปสู่การระบาดของโรคอ้วน เบาหวาน ความดัน และ NCD ทั่วโลก ที่เราเพิ่งจะเข้าใจกันวันนี้ว่ามีรากมาจาก “ปิรามิดคาร์บ” นั่นเอง
คำถามคือ ทำไมการกำหนดอาหารของอเมริกา (ซึ่งแน่นอนว่าแพร่กระจายไปทั่วโลกภายใต้ข้อกำหนดเดียวกัน) จึงเกิดขึ้นจาก "กระทรวงเกษตรสหรัฐอเมริกา" ไม่ใช่ หน่วยงานทางวิทยาศาสตร์ หรือ การแพทย์
หรือเพราะ “อาหาร” ในอเมริกา ไม่ได้เริ่มจากคำว่า “สุขภาพ” แต่เริ่มจาก “เศรษฐกิจ”
ย้อนกลับไปช่วงต้นศตวรรษที่ 20 โดยเฉพาะหลังสงครามโลกครั้งที่สอง สหรัฐฯ ต้องการฟื้นฟูเศรษฐกิจและผลักดันภาคการเกษตรให้โตอย่างรวดเร็ว โดยเฉพาะสินค้าพืชเชิงอุตสาหกรรม เช่น ข้าวโพด ข้าวสาลี ถั่วเหลือง นม และเนื้อจากฟาร์มอุตสาหกรรม และปากท้องของเกษตรกรคือฐานเสียงสำคัญในทุกๆรัฐบาล ดังนั้น USDA ซึ่งเป็นหน่วยงานที่ตั้งขึ้นเพื่อดูแลเกษตรกร จึงรับบทผู้ออก “แนวทางโภชนาการ” โดยเน้นว่า
อาหารอะไรที่ เกษตรกรผลิตได้เยอะ ก็เอามาดันให้ประชาชนกินเยอะ อาหารอะไรที่ ราคาถูก ผลิตได้เร็ว ก็นำมาใส่ไว้ฐานล่างของพีระมิด ให้ประชาชนกินเยอะ อาหารอะไรที่ มีอุตสาหกรรมอยู่เบื้องหลัง ก็เปิดประมูลให้มีบทบาทมากในการล็อบบี้นโยบาย ให้ประชาชนกินเยอะ
พูดง่ายๆ ก็คือ นโยบายอาหารอเมริกา ไม่ได้ออกโดยนักวิทยาศาสตร์หรือนักโภชนาการที่ไม่มีผลประโยชน์ทับซ้อน แต่มาจาก “ข้าราชการสายเกษตร+กลุ่มทุน” ที่ต้องการให้ภาคการเกษตรมีกำไรอย่างต่อเนื่อง และอย่าลืมว่า อเมริกา = โลก
แล้วหน่วยงานด้านวิทยาศาสตร์หรือแพทย์ เช่น NIH (National Institutes of Health) หรือ CDC (Centers for Disease Control and Prevention) หล่ะ แน่นอนครับว่ามีข้อมูลอยุ่ว่าก็มีสิทธิ์เสนอแนะอยู่บ้างแต่ทั้งหมดนี้ ไม่มีอำนาจออกนโยบายหลักที่ใช้จริงกับประชาชน ส่วนใหญ่แค่ให้ข้อมูลวิชาการ ซึ่งมักจะถูกลดทอนหรือละเลยเมื่อนโยบายจริงถูกเขียนขึ้นโดย USDA ในที่สุด
เมื่อเสียงของการตั้งคำถามเริ่มดังกว่าเสียงโฆษณา ขบวนการ “Low Carb” ก็เริ่มตั้งหลักและขยายวงกว้างอย่างเงียบๆ งานวิจัยใหม่ๆ เริ่มบ่งชี้ว่า “น้ำตาลและแป้ง” โดยเฉพาะแป้งแปรรูป คือภัยเงียบที่ส่งผลต่อการอักเสบเรื้อรัง ภาวะดื้ออินซูลิน และเมตาบอลิกซินโดรม จนกระทั่งช่วงต้นทศวรรษ 2010 เป็นต้นมา อาหารแนว “ลดคาร์บ เพิ่มไขมันดี เพิ่มโปรตีน” ก็กลายเป็นกระแสหลักขึ้นมา
ตอนนั้นหลายคนคิดว่า “พวกเราชนะแล้ว” โลกกลับมาฟังเสียงสุขภาพที่แท้จริง โปรตีนกลายเป็นคำตอบใหม่แห่งยุค
แต่มึงเอ๊ยยยยยย... เกมอาจไม่ได้จบตรงนั้น
เพราะในวันที่ประชาชนเริ่มหลีกหนีคาร์บ กลุ่มทุนอาหารข้ามชาติที่เคยวางรากอยู่ในอุตสาหกรรมแป้ง ได้ค่อยๆ แปรทิศ ย้ายการลงทุนไปสู่ “โปรตีนทางเลือก” รอไว้นานแล้วโดยที่เราไม่รู้ตัว ทั้งอาหารพืชแปรรูปอย่าง texture ถั่วเหลือง (TVP), โปรตีนจุลินทรีย์, เนื้อปลูกจากห้องแลบ ไปจนถึง “ไข่” และ “นม” ที่ไม่ได้มาจากสัตว์ โปรตีนสังเคราะห์ที่ผลิตโดยระบบชีวภาพวิศวกรรม (synthetic biology) ซึ่งได้รับเงินทุนจากบริษัทยักษ์ใหญ่อย่างต่อเนื่องตลอดสิบปีที่ผ่านมา
พอถึงวันโปรตีนกลายเป็นเทรนด์ เขาก็เข้ามาเป็นเจ้าของเทรนด์เป็นที่เรียบร้อยแล้ว พร้อมทุกอย่างแล้ว คำถามคือ ใครกันแน่ที่เป็น Trend Setter
โปรตีนจึงไม่ใช่เพียง “สารอาหาร” อีกต่อไป แต่มันคือ “สินค้าอนาคต” ที่สามารถควบคุมแหล่งผลิต แหล่งพันธุ์ เทคโนโลยีการแปรรูป และการกระจายผ่านแพลตฟอร์มค้าปลีกทั่วโลก และถ้าคุณสังเกต จะเห็นว่าไม่มีใครพูดถึง “คาร์บทางเลือก” หรือ "คาร์บเข้มข้น" หรือ "คาร์บที่ไม่ต้องใช้พืช" แม้แต่นิด ทั้งที่ในทางหลักการก็สามารถคิดค้นได้ไม่ต่างกัน แปลว่า พวกเขาไม่ได้แค่อยาก “เลิกขายคาร์บ” แต่กำลัง “เปลี่ยนสินค้าหลักใหม่” ให้ไปอยู่ในกลุ่มที่พวกเขาควบคุมได้ทั้งหมด แค่เอาคำว่า "โปรตีน" ขึ้นมาเป็นฉากหน้าไว้ก่อน
เริ่มเห็นภาพไหมครับ จากคาร์บที่เคยถูกบิดเบือน กลายมาเป็นโปรตีนที่ถูกเสนอให้เรายินดีรับอย่างไม่ตั้งคำถาม
“โปรตีนอนาคต” ดูเหมือนจะเป็นทางเลือก แต่จริงๆ แล้วอาจเป็นกับดักหรือเปล่า
วันนี้ที่หลายคนเฝ้ามองชัยชนะของผู้คนในการล้ม “ปิรามิดคาร์บ” แต่ไม่ทันเห็นว่ากำลังถูกลากเข้าสู่ “หอคอยโปรตีนจำลอง” ที่พวกเขาสร้างขึ้นใหม่ ด้วยบรรจุภัณฑ์สวยหรู คำว่า "รักษ์โลก" "ปลอดภัย" และ "ยั่งยืน" แต่แท้จริงคือห่วงโซ่ที่มัดให้เราเป็นเพียง “ผู้บริโภค” ที่ไม่มีทางรู้ว่าอาหารของเรามาจากธรรมชาติหรือห้องแลบอีกต่อไป เรากลายเป็นหนูที่ย้ายจากกล่องวงกตหนึ่ง มายังอีกกล่องวงกตหนึ่งหรือเปล่า เป็นคำถามที่ยังต้องตอบต่อไป
เฮียไม่ได้มาเพื่อหวาดระแวงนะครับ เพราะในเกมอำนาจอาหาร ไม่มีใครยอมเสียพื้นที่ พวกเขาแค่เปลี่ยนกลยุทธ์ เพื่อครองความเชื่อมั่นใหม่ ในชื่อ “โปรตีน” #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ e3ba5e1a:5e433365
2025-02-13 06:16:49
@ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get this line:
“Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.”
Yesterday, I came across a comment on the song Devil Went Down to Georgia that had a very similar feel to it:

America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans.
That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form.
For most countries, saying “our nation is the greatest” is, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people should be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence.
But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America.
That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is freedom. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit.
American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are definitionally better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.)
In Devil Went Down to Georgia, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.”
Libertas magnitudo est
-
 @ 57d1a264:69f1fee1
2025-05-12 07:27:52
@ 57d1a264:69f1fee1
2025-05-12 07:27:52A set of beautifully-designed, accessible components and a code distribution platform. Works with your favorite frameworks. Open Source. Open Code.
This is how @kurtispapple make use of it https://www.linkedin.com/pulse/championing-health-data-interoperability-my-journey-nz-kurtis-papple-mwglc
Start building yours at https://ui.shadcn.com/
originally posted at https://stacker.news/items/977930
-
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ 3d073b19:4ae60f39
2025-05-12 00:09:07
@ 3d073b19:4ae60f39
2025-05-12 00:09:07This is an English openletter
-
 @ e3ba5e1a:5e433365
2025-02-05 17:47:16
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a friendly discussion on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
- Unlike full single payer, individuals incur high costs
- Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
- Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
- Reduce regulations significantly.
-
In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
- Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
- Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-
 @ 57d1a264:69f1fee1
2025-05-12 06:41:49
@ 57d1a264:69f1fee1
2025-05-12 06:41:49It's incredible how deep people can go into something so mundane as a post stamp. Postage stamps are a surprisingly complex topic, overlapping with money, collectibility and bank notes. I was a postage stamp enthusiast myself, but this is one of those “the universe is surprisingly detailed” type. The rules defining postage and how it has been ruling commerce for centuries is even more fascinating and intriguing.
Discover more at https://www.linyangchen.com/Philately
originally posted at https://stacker.news/items/977918
-
 @ 91bea5cd:1df4451c
2025-02-04 17:24:50
@ 91bea5cd:1df4451c
2025-02-04 17:24:50Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ 91bea5cd:1df4451c
2025-02-04 17:15:57
@ 91bea5cd:1df4451c
2025-02-04 17:15:57Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ e39333da:7c66e53a
2025-05-12 00:03:18
@ e39333da:7c66e53a
2025-05-12 00:03:18::youtube{#VQRLujxTm3c}
Rockstar released the second trailer for Grand Theft Auto VI, where they mention that it showcases both cinematic and gameplay scenes equally, though of course it doesn't show any direct gameplay.
This trailer also announces the release date for the game. The game will come out on the 26th of May, 2026, for the PS5 and the Xbox One.
-
 @ e3ba5e1a:5e433365
2025-02-04 08:29:00
@ e3ba5e1a:5e433365
2025-02-04 08:29:00President Trump has started rolling out his tariffs, something I blogged about in November. People are talking about these tariffs a lot right now, with many people (correctly) commenting on how consumers will end up with higher prices as a result of these tariffs. While that part is true, I’ve seen a lot of people taking it to the next, incorrect step: that consumers will pay the entirety of the tax. I put up a poll on X to see what people thought, and while the right answer got a lot of votes, it wasn't the winner.

For purposes of this blog post, our ultimate question will be the following:
- Suppose apples currently sell for $1 each in the entire United States.
- There are domestic sellers and foreign sellers of apples, all receiving the same price.
- There are no taxes or tariffs on the purchase of apples.
- The question is: if the US federal government puts a $0.50 import tariff per apple, what will be the change in the following:
- Number of apples bought in the US
- Price paid by buyers for apples in the US
- Post-tax price received by domestic apple producers
- Post-tax price received by foreign apple producers
Before we can answer that question, we need to ask an easier, first question: before instituting the tariff, why do apples cost $1?
And finally, before we dive into the details, let me provide you with the answers to the ultimate question. I recommend you try to guess these answers before reading this, and if you get it wrong, try to understand why:
- The number of apples bought will go down
- The buyers will pay more for each apple they buy, but not the full amount of the tariff
- Domestic apple sellers will receive a higher price per apple
- Foreign apple sellers will receive a lower price per apple, but not lowered by the full amount of the tariff
In other words, regardless of who sends the payment to the government, both taxed parties (domestic buyers and foreign sellers) will absorb some of the costs of the tariff, while domestic sellers will benefit from the protectionism provided by tariffs and be able to sell at a higher price per unit.
Marginal benefit
All of the numbers discussed below are part of a helper Google Sheet I put together for this analysis. Also, apologies about the jagged lines in the charts below, I hadn’t realized before starting on this that there are some difficulties with creating supply and demand charts in Google Sheets.
Let’s say I absolutely love apples, they’re my favorite food. How much would I be willing to pay for a single apple? You might say “$1, that’s the price in the supermarket,” and in many ways you’d be right. If I walk into supermarket A, see apples on sale for $50, and know that I can buy them at supermarket B for $1, I’ll almost certainly leave A and go buy at B.
But that’s not what I mean. What I mean is: how high would the price of apples have to go everywhere so that I’d no longer be willing to buy a single apple? This is a purely personal, subjective opinion. It’s impacted by how much money I have available, other expenses I need to cover, and how much I like apples. But let’s say the number is $5.
How much would I be willing to pay for another apple? Maybe another $5. But how much am I willing to pay for the 1,000th apple? 10,000th? At some point, I’ll get sick of apples, or run out of space to keep the apples, or not be able to eat, cook, and otherwise preserve all those apples before they rot.
The point being: I’ll be progressively willing to spend less and less money for each apple. This form of analysis is called marginal benefit: how much benefit (expressed as dollars I’m willing to spend) will I receive from each apple? This is a downward sloping function: for each additional apple I buy (quantity demanded), the price I’m willing to pay goes down. This is what gives my personal demand curve. And if we aggregate demand curves across all market participants (meaning: everyone interested in buying apples), we end up with something like this:
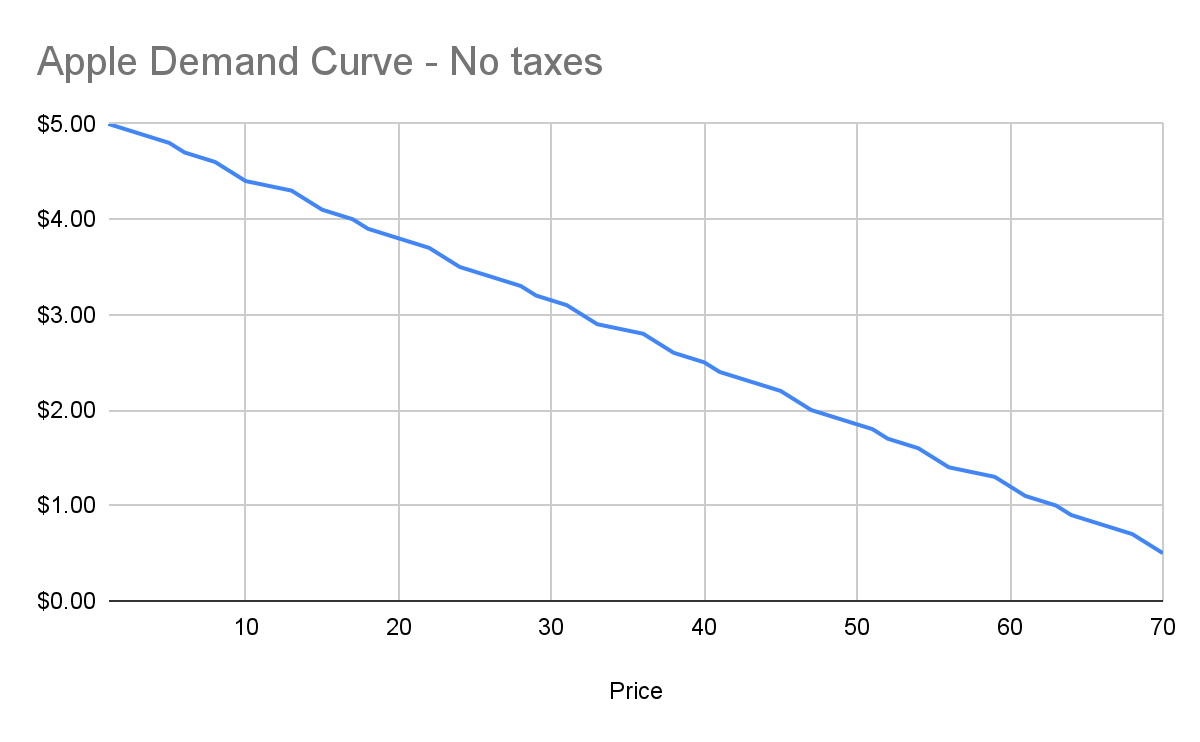
Assuming no changes in people’s behavior and other conditions in the market, this chart tells us how many apples will be purchased by our buyers at each price point between $0.50 and $5. And ceteris paribus (all else being equal), this will continue to be the demand curve for apples.
Marginal cost
Demand is half the story of economics. The other half is supply, or: how many apples will I sell at each price point? Supply curves are upward sloping: the higher the price, the more a person or company is willing and able to sell a product.
Let’s understand why. Suppose I have an apple orchard. It’s a large property right next to my house. With about 2 minutes of effort, I can walk out of my house, find the nearest tree, pick 5 apples off the tree, and call it a day. 5 apples for 2 minutes of effort is pretty good, right?
Yes, there was all the effort necessary to buy the land, and plant the trees, and water them… and a bunch more than I likely can’t even guess at. We’re going to ignore all of that for our analysis, because for short-term supply-and-demand movement, we can ignore these kinds of sunk costs. One other simplification: in reality, supply curves often start descending before ascending. This accounts for achieving efficiencies of scale after the first number of units purchased. But since both these topics are unneeded for understanding taxes, I won’t go any further.
Anyway, back to my apple orchard. If someone offers me $0.50 per apple, I can do 2 minutes of effort and get $2.50 in revenue, which equates to a $75/hour wage for me. I’m more than happy to pick apples at that price!
However, let’s say someone comes to buy 10,000 apples from me instead. I no longer just walk out to my nearest tree. I’m going to need to get in my truck, drive around, spend the day in the sun, pay for gas, take a day off of my day job (let’s say it pays me $70/hour). The costs go up significantly. Let’s say it takes 5 days to harvest all those apples myself, it costs me $100 in fuel and other expenses, and I lose out on my $70/hour job for 5 days. We end up with:
- Total expenditure: $100 + $70 * 8 hours a day * 5 days \== $2900
- Total revenue: $5000 (10,000 apples at $0.50 each)
- Total profit: $2100
So I’m still willing to sell the apples at this price, but it’s not as attractive as before. And as the number of apples purchased goes up, my costs keep increasing. I’ll need to spend more money on fuel to travel more of my property. At some point I won’t be able to do the work myself anymore, so I’ll need to pay others to work on the farm, and they’ll be slower at picking apples than me (less familiar with the property, less direct motivation, etc.). The point being: at some point, the number of apples can go high enough that the $0.50 price point no longer makes me any money.
This kind of analysis is called marginal cost. It refers to the additional amount of expenditure a seller has to spend in order to produce each additional unit of the good. Marginal costs go up as quantity sold goes up. And like demand curves, if you aggregate this data across all sellers, you get a supply curve like this:
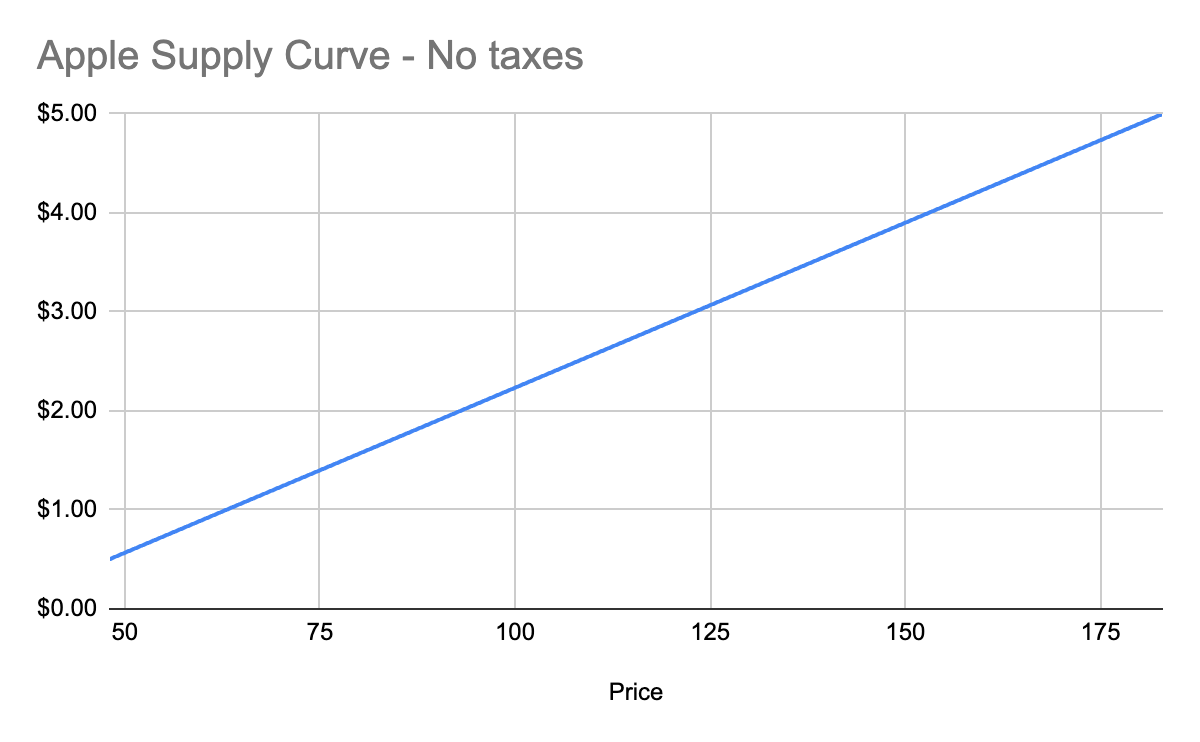
Equilibrium price
We now know, for every price point, how many apples buyers will purchase, and how many apples sellers will sell. Now we find the equilibrium: where the supply and demand curves meet. This point represents where the marginal benefit a buyer would receive from the next buyer would be less than the cost it would take the next seller to make it. Let’s see it in a chart:
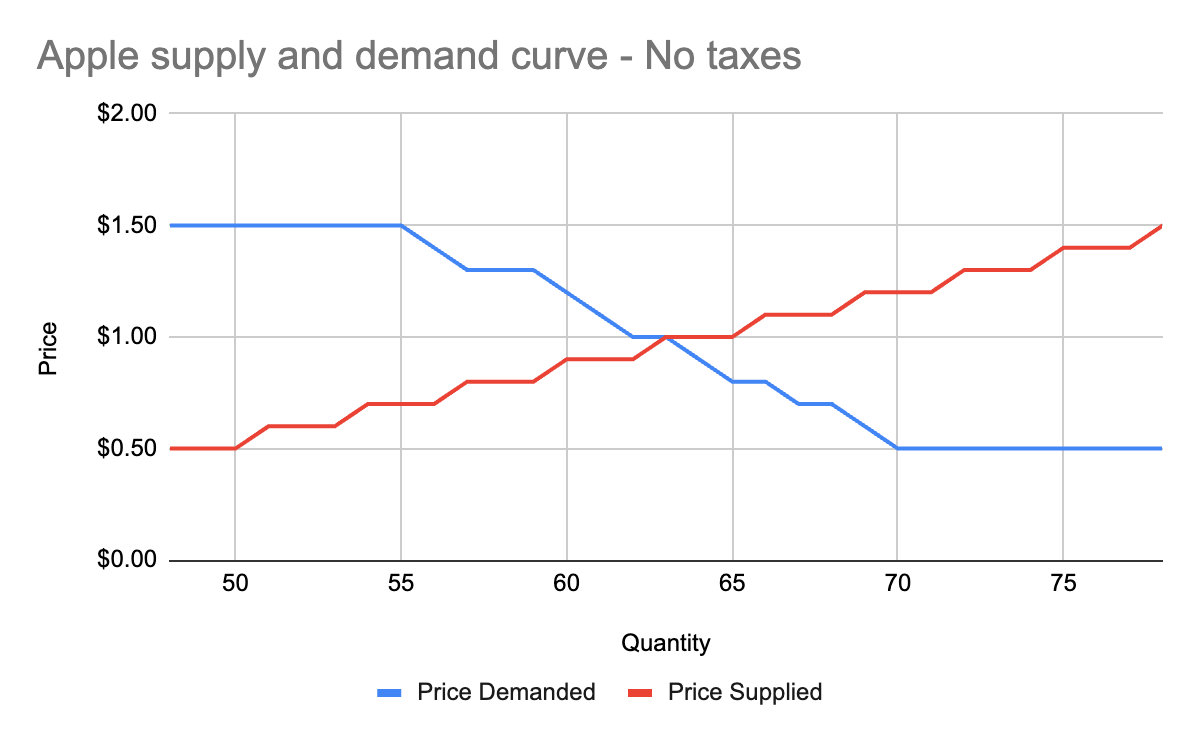
You’ll notice that these two graphs cross at the $1 price point, where 63 apples are both demanded (bought by consumers) and supplied (sold by producers). This is our equilibrium price. We also have a visualization of the surplus created by these trades. Everything to the left of the equilibrium point and between the supply and demand curves represents surplus: an area where someone is receiving something of more value than they give. For example:
- When I bought my first apple for $1, but I was willing to spend $5, I made $4 of consumer surplus. The consumer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and above the equilibrium price point.
- When a seller sells his first apple for $1, but it only cost $0.50 to produce it, the seller made $0.50 of producer surplus. The producer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and below the equilibrium price point.
Another way of thinking of surplus is “every time someone got a better price than they would have been willing to take.”
OK, with this in place, we now have enough information to figure out how to price in the tariff, which we’ll treat as a negative externality.
Modeling taxes
Alright, the government has now instituted a $0.50 tariff on every apple sold within the US by a foreign producer. We can generally model taxes by either increasing the marginal cost of each unit sold (shifting the supply curve up), or by decreasing the marginal benefit of each unit bought (shifting the demand curve down). In this case, since only some of the producers will pay the tax, it makes more sense to modify the supply curve.
First, let’s see what happens to the foreign seller-only supply curve when you add in the tariff:
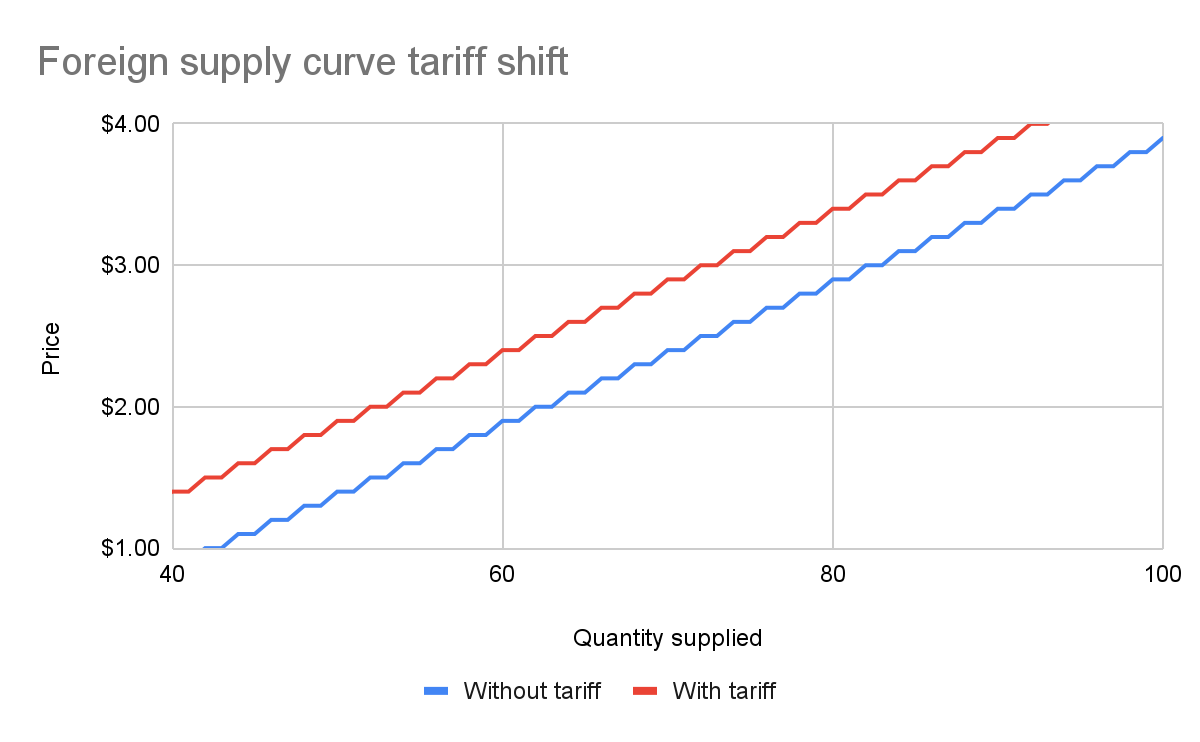
With the tariff in place, for each quantity level, the price at which the seller will sell is $0.50 higher than before the tariff. That makes sense: if I was previously willing to sell my 82nd apple for $3, I would now need to charge $3.50 for that apple to cover the cost of the tariff. We see this as the tariff “pushing up” or “pushing left” the original supply curve.
We can add this new supply curve to our existing (unchanged) supply curve for domestic-only sellers, and we end up with a result like this:
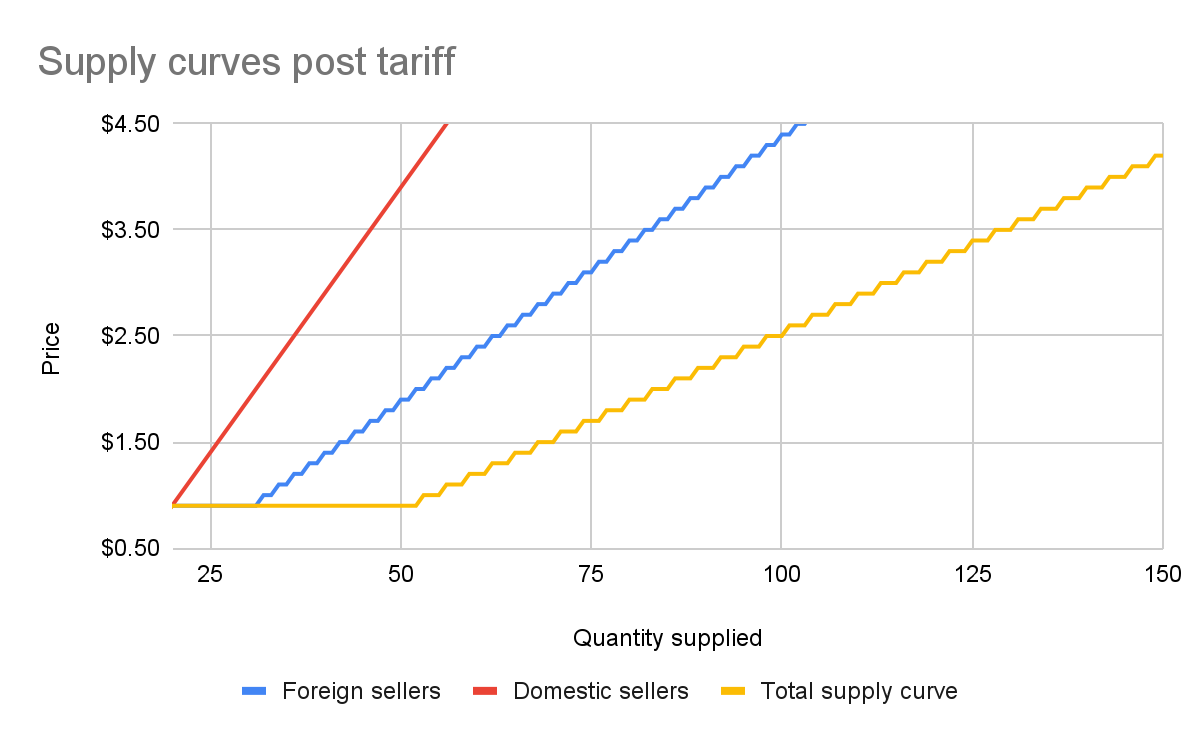
The total supply curve adds up the individual foreign and domestic supply curves. At each price point, we add up the total quantity each group would be willing to sell to determine the total quantity supplied for each price point. Once we have that cumulative supply curve defined, we can produce an updated supply-and-demand chart including the tariff:
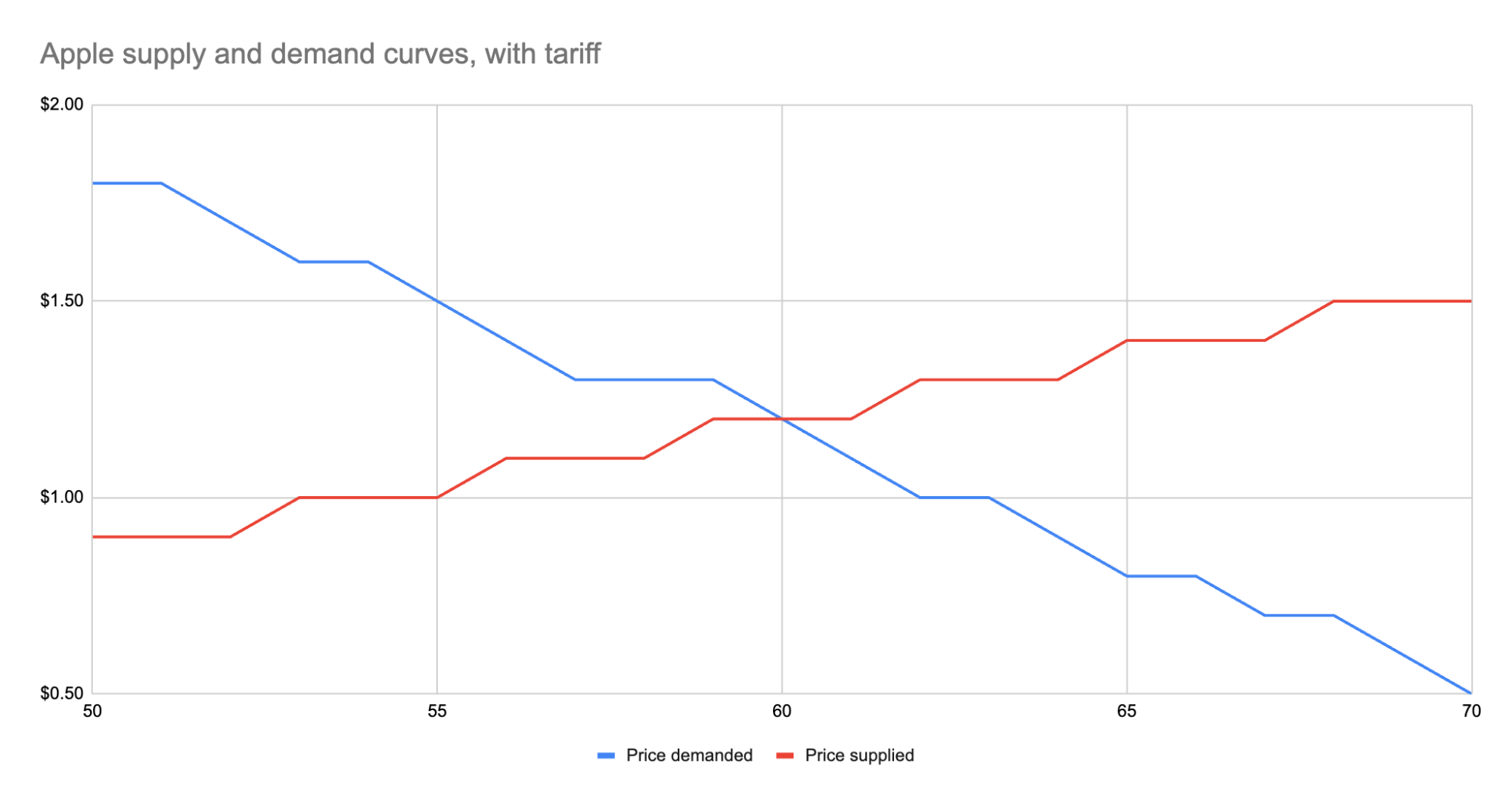
As we can see, the equilibrium has shifted:
- The equilibrium price paid by consumers has risen from $1 to $1.20.
- The total number of apples purchased has dropped from 63 apples to 60 apples.
- Consumers therefore received 3 less apples. They spent $72 for these 60 apples, whereas previously they spent $63 for 3 more apples, a definite decrease in consumer surplus.
- Foreign producers sold 36 of those apples (see the raw data in the linked Google Sheet), for a gross revenue of $43.20. However, they also need to pay the tariff to the US government, which accounts for $18, meaning they only receive $25.20 post-tariff. Previously, they sold 42 apples at $1 each with no tariff to be paid, meaning they took home $42.
- Domestic producers sold the remaining 24 apples at $1.20, giving them a revenue of $28.80. Since they don’t pay the tariff, they take home all of that money. By contrast, previously, they sold 21 apples at $1, for a take-home of $21.
- The government receives $0.50 for each of the 60 apples sold, or in other words receives $30 in revenue it wouldn’t have received otherwise.
We could be more specific about the surpluses, and calculate the actual areas for consumer surplus, producer surplus, inefficiency from the tariff, and government revenue from the tariff. But I won’t bother, as those calculations get slightly more involved. Instead, let’s just look at the aggregate outcomes:
- Consumers were unquestionably hurt. Their price paid went up by $0.20 per apple, and received less apples.
- Foreign producers were also hurt. Their price received went down from the original $1 to the new post-tariff price of $1.20, minus the $0.50 tariff. In other words: foreign producers only receive $0.70 per apple now. This hurt can be mitigated by shifting sales to other countries without a tariff, but the pain will exist regardless.
- Domestic producers scored. They can sell less apples and make more revenue doing it.
- And the government walked away with an extra $30.
Hopefully you now see the answer to the original questions. Importantly, while the government imposed a $0.50 tariff, neither side fully absorbed that cost. Consumers paid a bit more, foreign producers received a bit less. The exact details of how that tariff was split across the groups is mediated by the relevant supply and demand curves of each group. If you want to learn more about this, the relevant search term is “price elasticity,” or how much a group’s quantity supplied or demanded will change based on changes in the price.
Other taxes
Most taxes are some kind of a tax on trade. Tariffs on apples is an obvious one. But the same applies to income tax (taxing the worker for the trade of labor for money) or payroll tax (same thing, just taxing the employer instead). Interestingly, you can use the same model for analyzing things like tax incentives. For example, if the government decided to subsidize domestic apple production by giving the domestic producers a $0.50 bonus for each apple they sell, we would end up with a similar kind of analysis, except instead of the foreign supply curve shifting up, we’d see the domestic supply curve shifting down.
And generally speaking, this is what you’ll always see with government involvement in the economy. It will result in disrupting an existing equilibrium, letting the market readjust to a new equilibrium, and incentivization of some behavior, causing some people to benefit and others to lose out. We saw with the apple tariff, domestic producers and the government benefited while others lost.
You can see the reverse though with tax incentives. If I give a tax incentive of providing a deduction (not paying income tax) for preschool, we would end up with:
- Government needs to make up the difference in tax revenue, either by raising taxes on others or printing more money (leading to inflation). Either way, those paying the tax or those holding government debased currency will pay a price.
- Those people who don’t use the preschool deduction will receive no benefit, so they simply pay a cost.
- Those who do use the preschool deduction will end up paying less on tax+preschool than they would have otherwise.
This analysis is fully amoral. It’s not saying whether providing subsidized preschool is a good thing or not, it simply tells you where the costs will be felt, and points out that such government interference in free economic choice does result in inefficiencies in the system. Once you have that knowledge, you’re more well educated on making a decision about whether the costs of government intervention are worth the benefits.
-
 @ 3d073b19:4ae60f39
2025-05-11 23:59:56
@ 3d073b19:4ae60f39
2025-05-11 23:59:56Heading 1
Heading 2
Heading 3
Heading 4
Heading 5
Heading 6
Lists
Unordered List
- Item 1
- Item 2
- Subitem 2.1
- Subitem 2.2
Ordered List
- First item
- Second item
- Third item
Links
OpenAI - A link to OpenAI's website. Markdown Guide - A comprehensive guide to Markdown syntax.
Images
 - An example image with a title.
- An example image with a title.Blockquotes
This is a blockquote. It can span multiple lines. It is often used to highlight important information or quotes.
Code
Inline Code
Here is some
inline codethat demonstrates how to format code within a sentence.Code Block
```python
This is a Python code block
def hello_world(): print("Hello, world!") ```
Emphasis
Bold
This text is bold. This text is also bold.
Italic
This text is italic. This text is also italic.
Strikethrough
~~This text is strikethrough.~~
-
 @ 9c9d2765:16f8c2c2
2025-05-12 05:15:47
@ 9c9d2765:16f8c2c2
2025-05-12 05:15:47CHAPTER SIXTEEN
Mr. JP sat up abruptly as his phone buzzed. It was an anonymous message. He opened it slowly, his eyes scanning the contents with growing disbelief.
"James has returned to JP Enterprises. Charles reinstated him. He’s now President of your company."
His blood ran cold.
Mrs. JP saw the tension in his expression. "What’s wrong?"
"He’s back," Mr. JP said grimly. "Our son. James. He's taken over the company."
He stared into space, his mind reeling. "And Charles helped him..."
They had spent years trying to distance themselves from the disgrace of James’s past only to now be faced with the reality that he had clawed his way back into the empire they built.
The anonymous message was, of course, sent by Mark and Helen, each relishing in the chaos they had ignited. With the scandalous file now in their hands and James’s own family unknowingly brought into the picture, they believed the final blow was in place.
Mark leaned back in his chair and smiled as he read the forwarded documents.
"Let’s see how your so-called empire stands after this, James," he said quietly.
Helen, standing beside him, added coldly, "This time, he won’t survive it."
"How could he do this?" Mr. JP muttered under his breath, clutching his phone tightly. "How could Charles go behind my back and reinstall him? My own brother..."
The news that James had returned to JP Enterprises and not just as a member, but as its President had shaken him to the core. But what stung more was the betrayal he felt from Charles, who had once promised never to interfere in the matter again.
Fuming with rage and disbelief, Mr. JP boarded the next flight back home. Upon arrival, he didn’t even stop by the family estate. Instead, he went straight to the Regency Grand, the city’s most luxurious hotel, the same place he used to spend time with his family during better days. He booked the presidential suite and immediately dialed Charles' number.
"Meet me. Now. At the hotel," he barked before ending the call without waiting for a response.
Within the hour, Charles walked in, calm but aware of the storm brewing.
"You defied me, Charles," Mr. JP said, his voice icy. "You brought back the one person I had removed. The one person I swore would never set foot in the company again."
"Because you were wrong," Charles replied firmly. "You made a decision based on lies."
Mr. JP’s glare deepened.
"Lies? The records were clear embezzlement. Theft. He disgraced this family, Charles!"
Charles stood his ground. "Those records were manipulated. You never gave James a chance to explain himself."
He stepped closer. "The funds he was accused of stealing? He used them to invest in a struggling tech start-up that exploded in value two years later. That investment saved JP Enterprises during the economic downturn. The company is standing today because of James’s vision and sacrifice."
Silence filled the room.
Mr. JP felt his heart sink as the weight of Charles’s words settled in. He turned away, walking slowly to the window, staring out at the city skyline.
"All this time... I condemned my own son... exiled him... because I trusted false reports?"
Charles nodded. "Yes. And despite it all, he returned not for revenge, but to help us."
Tears welled up in Mr. JP’s eyes. His pride, once like stone, was now crumbling.
Without hesitation, he picked up his phone and dialed James’s number. The phone rang twice before James answered.
"Hello?" came the familiar voice, calm and distant.
"James... it’s your father." His voice trembled. "I... I’m sorry. I was wrong. Gravely wrong. Everything I believed about you was a lie. I let you down, son."
There was silence on the other end.
"I just found out the truth," Mr. JP continued. "And I’m proud of what you’ve done for the company, for our name. I want you to know... you are reinstated as the rightful heir to JP Enterprises. I want you back not just as President, but as my son."
James took a long pause before answering.
"It took you long enough," he said softly. "But... thank you."
Though James had once sworn not to seek his parents' approval, deep down, those words still mattered. And hearing them from the father who had disowned him brought a quiet sense of closure.
The rift that had torn them apart for years was beginning to heal.
"Dad, who told you I was the President of JP Enterprises?" James asked, his tone calm but firm as he stood before his father in the grand office of the family estate.
Mr. JP, still adjusting to the emotional weight of his recent apology, furrowed his brow. "It was anonymous, son. I received a message with no name, no clue. Just the information."
James narrowed his eyes. "Can you forward the message to me?"
"Of course," his father replied, pulling out his phone. Within seconds, the message was in James’s inbox.
Later that evening, James sat in his private office, staring at the message on his screen. Something about it felt off too calculated, too timely. He forwarded it to his personal cybersecurity team with one instruction: “Trace the source. I want to know everything about who sent it, how, and if they’re working with someone.”
Meanwhile, Ray Enterprises was thriving again under James’s investment. With the influx of capital and revitalized operations, profits were skyrocketing. However, while the company’s success looked promising on the surface, the Ray family was barely reaping the rewards.
James’s 85% share ensured he collected the lion’s portion of every deal. Robert, despite being the figurehead chairman, found himself managing a flourishing empire but receiving only crumbs in return.
Frustrated and desperate, Robert scheduled a private meeting with James.
"James, please... eighty-five percent is bleeding us dry. We’re grateful for what you’ve done truly but surely we can renegotiate?"
James leaned back in his chair, expression unreadable. "You signed the agreement, Robert. You knew the terms. And frankly, I'm not in the mood to revisit old conversations."
"We just want fairness," Robert pleaded. "A little breathing space"
"If this discussion continues," James interrupted coldly, "I’ll pull out my funds. And when I do, I promise Ray Enterprises will go down faster than it rose. Do I make myself clear?"
Robert’s face fell. He had no choice but to nod and walk away, defeated.
Two weeks later, James’s cybersecurity team sent their report. The source of the anonymous message had been traced and the result was both surprising and telling.
Tracy.
James sat silently as he read the details. Tracy, his own subordinate, had accessed restricted files from the company’s internal network. It wasn’t just a case of whistleblowing it was deliberate sabotage. But what intrigued him more was the fact that she had gone to great lengths to cover her tracks.
No one takes that risk alone, he thought.
Despite having the evidence in hand, James chose silence. Not out of mercy but strategy. He needed to know who she was working with. Who else had a vested interest in his downfall?
-
 @ 3d073b19:4ae60f39
2025-05-11 23:52:28
@ 3d073b19:4ae60f39
2025-05-11 23:52:28Headings
Heading 1
Heading 2
Heading 3
Heading 4
Heading 5
Heading 6
Lists
Unordered List
- Item 1
- Item 2
- Subitem 2.1
- Subitem 2.2
Ordered List
- First item
- Second item
- Third item
Mixed List
-
Item 1
-
Item 2
-
Item 3
Links
OpenAI - A link to OpenAI's website. Markdown Guide - A comprehensive guide to Markdown syntax.
Images
 - An example image with a title.
- An example image with a title.Blockquotes
This is a blockquote. It can span multiple lines. It is often used to highlight important information or quotes.
Code
Inline Code
Here is some
inline codethat demonstrates how to format code within a sentence.Code Block
```python
This is a Python code block
def hello_world(): print("Hello, world!") ```
Emphasis
Bold
This text is bold. This text is also bold.
Italic
This text is italic. This text is also italic.
Strikethrough
~~This text is strikethrough.~~
-
 @ 97c70a44:ad98e322
2025-01-30 17:15:37
@ 97c70a44:ad98e322
2025-01-30 17:15:37There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test.
In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go.
It uses nostr
The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol.
Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key.
In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along.
In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim.
It leverages nostr
Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app".
This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back.
Some examples might include:
- Using nostr signers to encrypt or sign data, and then store that data on a proprietary server.
- Using nostr relays as a kind of low-code backend, but using proprietary event payloads.
- Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you.
An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem.
In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering.
It complements nostr
Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role.
One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense.
Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)?
A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs.
To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen.
It embodies nostr
Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate.
This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product?
To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the protocol, while apps that benefit nostr exclusively via network effect are integrated into nostr the network. An app that does both things is working in symbiosis with nostr as a whole.
An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem:
- In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors.
- In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for.
Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency as nostr users.
If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states:
Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions.
These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers.
As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria.
Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type".
To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well,
- There is a spec for forms and responses, which means that...
- Multiple clients can implement the same data format, allowing for credible exit and user choice, even of...
- Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does...
- Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to...
- Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost".
Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr.
It supports nostr
Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually).
This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content?
In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together.
A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own.
So while I might hesitate to call many of these things "apps", they are certainly "nostr".
Appendix: it smells like a NINO
So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr.
You app might be a NINO if:
- There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind)
- There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository)
- Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr
- Your NIP relies on trusted third (or first) parties
- There's only one implementation of your NIP (yours)
- Your core value proposition doesn't depend on relays, events, or nostr identities
- One or more relay urls are hard-coded into the source code
- Your app depends on a specific relay implementation to work (ahem, relay29)
- You don't validate event signatures
- You don't publish events to relays you don't control
- You don't read events from relays you don't control
- You use legacy web services to solve problems, rather than nostr-native solutions
- You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app
- You don't use NIP 89 to discover clients and services
- You haven't published a NIP 89 listing for your app
- You don't leverage your users' web of trust for filtering out spam
- You don't respect your users' mute lists
- You try to "own" your users' data
Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product.
If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation:
- Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine.
- Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc.
- Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats.
- Think your idea is a good one? Talk to other devs or open a PR to the nips repo. No one can adopt your NIP if they don't know about it.
- Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated.
- Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask!
I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV.
-
 @ d7955b22:025a3ba9
2025-05-12 04:31:36
@ d7955b22:025a3ba9
2025-05-12 04:31:36O mundo dos jogos online tem se expandido rapidamente, oferecendo uma infinidade de opções para os jogadores. Entre as diversas plataformas disponíveis, o 99bra se destaca por sua variedade de opções e a experiência de usuário única que proporciona. Este artigo oferece uma visão detalhada sobre o que o 99bra tem a oferecer, desde suas características gerais até a experiência de jogo que promete satisfazer todos os tipos de jogadores.
Introdução à Plataforma 99bra 99bra é uma plataforma de entretenimento digital voltada para os entusiastas de jogos online. Com um design intuitivo e uma interface amigável, a plataforma foi criada para oferecer uma experiência de navegação fluida, seja em desktop ou dispositivos móveis. A plataforma se destaca pela sua confiabilidade e pela qualidade dos jogos oferecidos, sempre priorizando a segurança e a proteção dos dados de seus usuários.
Ao se cadastrar no 99bra, os jogadores têm acesso a uma ampla gama de opções de jogos, desde clássicos até lançamentos inovadores. O site se adapta às necessidades dos usuários, com suporte em português e atendimento ao cliente de excelência, tornando a plataforma acessível a jogadores de todas as idades e níveis de experiência. O processo de inscrição é rápido e simples, permitindo que os novos usuários comecem a se divertir em poucos minutos.
A Variedade de Jogos no 99bra O que realmente chama a atenção no 99bra é a diversidade de jogos oferecidos. A plataforma conta com uma vasta seleção de títulos, abrangendo uma ampla gama de gêneros. Seja você um fã de jogos de mesa, slots ou apostas esportivas, o 99bra tem algo para todos. Cada categoria de jogo é desenvolvida para garantir jogabilidade envolvente, gráficos impressionantes e uma experiência imersiva.
Jogos de Mesa Os jogos de mesa são um dos maiores atrativos da plataforma, com várias opções que incluem clássicos como blackjack, roleta e baccarat. Estes jogos oferecem uma experiência realista e dinâmica, com a possibilidade de interagir com outros jogadores. A interface é cuidadosamente projetada para garantir que cada clique e movimento se sinta natural, criando uma atmosfera que lembra a de um ambiente de jogo físico.
Slots e Máquinas de Vídeo Para os amantes das máquinas de vídeo, o 99bra oferece uma impressionante coleção de slots. Os jogadores podem explorar uma variedade de temas, desde aventuras épicas até histórias de fantasia, com gráficos vibrantes e animações cativantes. As funções de bônus, rodadas grátis e jackpots progressivos tornam os jogos ainda mais emocionantes, com a possibilidade de grandes vitórias a cada giro.
Apostas Esportivas Outro ponto forte da plataforma são as apostas esportivas. O 99bra oferece uma extensa seleção de esportes para os fãs de esportes ao vivo. Seja futebol, basquete, tênis ou eSports, a plataforma proporciona odds competitivas e a chance de apostar em eventos de todo o mundo, com atualizações em tempo real para garantir que o jogador esteja sempre informado.
A Experiência do Jogador A experiência do jogador é o aspecto que diferencia o 99bra de outras plataformas. Desde o momento do cadastro até as interações durante os jogos, a plataforma é projetada para oferecer facilidade, conforto e diversão sem interrupções. O 99bra é otimizado para fornecer uma navegação rápida e sem erros, com um layout que garante que o jogador possa acessar todos os jogos e funcionalidades de forma simples.
Além disso, a plataforma oferece recursos adicionais para tornar a experiência ainda mais envolvente. Os jogadores podem configurar preferências de jogo, participar de promoções exclusivas e interagir com outros jogadores, criando uma verdadeira comunidade. A segurança também é uma prioridade, com criptografia de dados avançada e processos de verificação para garantir que todas as transações e informações pessoais estejam protegidas.
Suporte ao Cliente O suporte ao cliente do 99bra é excepcional. A plataforma oferece múltiplos canais de atendimento, incluindo chat ao vivo, e-mail e telefone, para que os jogadores possam obter assistência rápida sempre que necessário. A equipe de suporte é altamente treinada e pronta para resolver qualquer dúvida ou problema de forma eficiente, garantindo que a experiência do jogador nunca seja comprometida.
Conclusão O 99bra é uma plataforma completa que atende aos mais altos padrões de qualidade e segurança no universo dos jogos online. Com uma vasta seleção de jogos, suporte ao cliente de excelência e uma experiência de usuário impecável, o 99bra se consolida como uma das opções mais atrativas para quem busca diversão e entretenimento. Se você está procurando uma plataforma que combine inovação, variedade e uma jogabilidade envolvente, o 99bra certamente é uma excelente escolha.
-
 @ d7955b22:025a3ba9
2025-05-12 04:31:00
@ d7955b22:025a3ba9
2025-05-12 04:31:00A plataforma 53a é uma das mais novas e emocionantes opções para quem busca uma experiência completa de entretenimento digital. Com uma ampla gama de jogos e funcionalidades voltadas para o prazer e a diversão dos jogadores, a 53a se destaca por sua interface intuitiva, seu foco na segurança e uma vasta gama de opções para todos os gostos. Se você ainda não conhece essa plataforma inovadora, continue lendo e descubra tudo o que ela tem a oferecer!
Introdução à Plataforma 53a A 53a é uma plataforma de entretenimento online que se destaca pelo seu compromisso em oferecer uma experiência única aos jogadores. Com um design moderno e acessível, a plataforma foi criada para atender a um público que busca algo mais do que simples joguinhos – ela oferece uma verdadeira imersão em um universo de possibilidades.
Ao acessar a 53a , os usuários são rapidamente apresentados a um painel de controle simplificado, onde podem facilmente navegar por diferentes categorias de jogos, conferir promoções e acessar uma série de recursos exclusivos. Além disso, a plataforma está disponível em diversos dispositivos, incluindo desktop, smartphones e tablets, permitindo que o jogador tenha acesso à diversão em qualquer lugar e a qualquer momento.
Jogos Empolgantes para Todos os Gostos A 53a não se limita a um único tipo de jogo. Em vez disso, oferece uma vasta gama de opções, com títulos que atendem a diferentes preferências e estilos de jogo. Desde jogos de habilidade, como jogos de mesa e jogos de cartas, até opções mais interativas e imersivas, como máquinas de diversão, a plataforma tem algo para todos os jogadores.
Jogos de Mesa e Cartas: Para os que apreciam uma experiência mais estratégica, a 53a oferece uma seleção diversificada de jogos de mesa, incluindo opções clássicas como o blackjack, pôquer e roleta. Cada jogo é projetado para proporcionar uma experiência desafiadora e envolvente, com gráficos impressionantes e uma jogabilidade fluida.
Máquinas de Diversão: Para quem busca uma experiência mais dinâmica e de fácil acesso, as máquinas de diversão são a escolha perfeita. Com uma vasta gama de temas e estilos, essas máquinas são ideais para momentos de descontração, com rodadas rápidas e prêmios atrativos. Cada jogo tem sua própria atmosfera única, com sons e animações que mantêm o jogador imerso por horas.
Jogos ao Vivo: Uma das grandes atrações da 53a são os jogos ao vivo, onde os jogadores podem interagir em tempo real com dealers e outros participantes. Esses jogos trazem a emoção de uma experiência presencial, mas com a conveniência de estar em casa ou onde preferir.
A Experiência do Jogador na 53a A experiência do jogador na plataforma 53a é pensada para ser fluida, segura e divertida. Com uma interface simples, os jogadores podem facilmente acessar seus jogos favoritos e navegar por outras funcionalidades da plataforma.
Interface Intuitiva: Desde o momento em que você entra na 53a, perceberá como a plataforma foi projetada com o usuário em mente. O layout claro e as opções bem definidas tornam a navegação fácil, mesmo para aqueles que não são tão familiarizados com plataformas digitais.
Segurança e Privacidade: A plataforma 53a adota as melhores práticas de segurança para garantir que todas as informações dos jogadores sejam protegidas. Desde transações financeiras até dados pessoais, a 53a utiliza tecnologias avançadas de criptografia para garantir que seus dados estejam sempre seguros.
Atendimento ao Cliente: A 53a se destaca também pelo seu excelente suporte ao cliente. Caso o jogador tenha alguma dúvida ou precise de ajuda, pode contar com uma equipe de atendimento pronta para oferecer assistência de forma rápida e eficaz. A plataforma também conta com uma seção de perguntas frequentes (FAQ) que ajuda a esclarecer as dúvidas mais comuns.
Conclusão A plataforma 53a se consolida como uma das principais opções de entretenimento online para quem busca diversão, segurança e uma experiência de usuário completa. Com uma grande variedade de jogos, suporte de alta qualidade e uma interface amigável, ela atende às necessidades de todos os tipos de jogadores, proporcionando momentos inesquecíveis. Se você está à procura de uma plataforma inovadora, segura e divertida, a 53a é a escolha certa para você!
-
 @ 3c389c8f:7a2eff7f
2025-05-11 22:53:30
@ 3c389c8f:7a2eff7f
2025-05-11 22:53:30As I'm sitting here trying to hone in on what might be important to write about in this moment, my mind keeps swirling around through all the things that have me sitting here to begin with. Nostr found me in a time when my life needed a change. The discovery of something that provided the light of hope to an otherwise dark, dystopian future was more powerful than I could have ever predicted. Timing is everything, they say. I believe that to be half true, as timing alone means nothing if the will is non-existent. The intersection of opportunity and preparedness, and all that. I know how I found my way here, but I do not fully understand the things that have drawn my curiosity and kept my attention so strongly. My will ached for change, simplicity, and meaning. I found it, in what seem to me, simultaneously the most likely and the most unlikely of places. There's a magic to that, and its probably better to leave some questions unanswered, lest they lose their mystic power.
My experiences are my own but theme of them resonates through most of the people with whom I interact. It's been very clear that I wasn't alone in these feelings. A movement of highly inspired, hopeful people have continued to support this digital freedom movement since my arrival, in varying ways. Some people have highly technical skills ranging from network systems to design to cybersecurity. Others, like myself, have little to offer in the realms of functionality and we do what we can to breathe life into the systems built to provide digital freedom of speech for all. It's a humbling experience. We are reminded. sometimes directly and sometimes indirectly, that none of Nostr would matter if there were no one using it. We know this to be true, but it is no less humbling to be surrounded by constant innovation and a thriving desire to bring this experience to the entire world.
Now here I sit, tapping out these words, in the midst of another massive life change, stressful but chosen. I could sign off, go read a book in the garden, and go about my world as I would have in my pre-Nostr times. I don't want to do that, though. Hope is here. If there is a place to dwell, in hope is where I will always choose.
I find it important to acknowledge, though, that Nostr and the people using it are in a constant state of flux, too. This isn't my rock nor harbor nor shelter. It's the chaotic good, reminding me both to keep an appreciation for how far this ecosystem has come in such a short amount of time and a realistic set of expectations for where this all can go. The same applies for how well things work at any given moment...And equally so in missing my some of my early Nostr friends that have come and gone, while remaining open to the possibility of meeting new ones... Experiences had and experiences yet to come. I don't know if I have ever been so coaxed outside of my mind by a group of strangers on the internet. But here I am, looking back and looking forward, surrounded by awe in all directions, sharing thoughts that would otherwise be scribbled in pen to be burned in a random evening fire. I've long felt that the core of social media should be just this. Spaces for people to connect, above all else, in the ways that create meaning in our lives. I suppose in some ways that did exist before, but it was twisted, and obscured, and slowly pulled away.
Now its here and super-charged by possibility. What this looks like for any individual will not be the same as my own view. That's part of what makes this so beautiful to me. We need to be able to speak freely. Just as importantly we need to be able to surround ourselves with the things and people that makes us want to do more, that make us want to feel humbled. Or not, if we so choose... but I choose hope.
-
 @ 9e69e420:d12360c2
2025-01-30 12:23:04
@ 9e69e420:d12360c2
2025-01-30 12:23:04Tech stocks have taken a hit globally after China's DeepSeek launched a competitive AI chatbot at a much lower cost than US counterparts. This has stirred market fears of a $1.2 trillion loss across tech companies when trading opens in New York.
DeepSeek’s chatbot quickly topped download charts and surprised experts with its capabilities, developed for only $5.6 million.
The Nasdaq dropped over 3% in premarket trading, with major firms like Nvidia falling more than 10%. SoftBank also saw losses shortly after investing in a significant US AI venture.
Venture capitalist Marc Andreessen called it “AI’s Sputnik moment,” highlighting its potential impact on the industry.
![] (https://www.telegraph.co.uk/content/dam/business/2025/01/27/TELEMMGLPICT000409807198_17379939060750_trans_NvBQzQNjv4BqgsaO8O78rhmZrDxTlQBjdGLvJF5WfpqnBZShRL_tOZw.jpeg)
-
 @ 9e69e420:d12360c2
2025-01-30 12:13:39
@ 9e69e420:d12360c2
2025-01-30 12:13:39Salwan Momika, a Christian Iraqi known for burning the Koran in Sweden, was shot dead during a TikTok livestream in an apartment in Sodertalje. The 38-year-old sparked outrage in the Muslim community for his demonstrations, leading to global condemnation. After being rushed to the hospital, he was pronounced dead.
Authorities arrested five individuals in connection with the incident. Momika's death comes days before a court ruling on his possible incitement of ethnic hatred. The incident highlights the tensions surrounding free speech and religious sentiments, intensifying after his controversial protests in 2023.
-
 @ bf47c19e:c3d2573b
2025-05-11 22:33:46
@ bf47c19e:c3d2573b
2025-05-11 22:33:46Originalni tekst na dvadesetjedan.com
Autor: Vijay Boyapati / Prevod na hrvatski: Matija
Sa zadnjim cijenama koje je bitcoin dosegao 2017., optimističan scenarij za ulagače se možda čini toliko očitim da ga nije potrebno niti spominjati. Alternativno, možda se nekome čini glupo ulagati u digitalnu vrijednost koja ne počiva na nijednom fizičkom dobru ili vladi i čiji porast cijene su neki usporedili sa manijom tulipana ili dot-com balonom. Nijedno nije točno; optimističan scenarij za Bitcoin je uvjerljiv, ali ne i očit. Postoje značajni rizici kod ulaganja u Bitcoin, no, kao što planiram pokazati, postoji i ogromna prilika.
Geneza
Nikad u povijesti svijeta nije bilo moguće napraviti transfer vrijednosti među fizički udaljenim ljudima bez posrednika, poput banke ili vlade. 2008. godine, anonimni Satoshi Nakamoto je objavio 8 stranica rješenja na dugo nerješivi računalski problem poznat kao “Problem Bizantskog Generala.” Njegovo rješenje i sustav koji je izgradio - Bitcoin - dozvolio je, prvi put ikad, da se vrijednost prenosi brzo i daleko, bez ikakvih posrednika ili povjerenja. Implikacije kreacije Bitcoina su toliko duboke, ekonomski i računalski, da bi Nakamoto trebao biti prva osoba nominirana za Nobelovu nagradu za ekonomiju i Turingovu nagradu.
Za ulagače, važna činjenica izuma Bitcoina (mreže i protokola) je stvaranje novog oskudnog digitalnog dobra - bitcoina (monetarne jedinice). Bitcoini su prenosivi digitalni “novčići” (tokeni), proizvedeni na Bitcoin mreži kroz proces nazvan “rudarenje” (mining). Rudarenje Bitcoina je ugrubo usporedivo sa rudarenjem zlata, uz bitnu razliku da proizvodnja bitcoina prati unaprijed osmišljeni i predvidivi raspored. Samo 21 milijun bitcoina će ikad postojati, i većina (2017., kada je ovaj tekst napisan) su već izrudareni. Svake četiri godine, količina rudarenih bitcoina se prepolovi. Produkcija novih bitcoina će potpuno prestati 2140. godine.
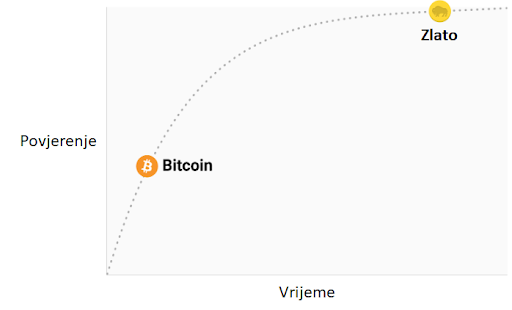 Stopa inflacije —— Monetarna baza
Stopa inflacije —— Monetarna bazaBitcoine ne podržava nikakva roba ili dobra, niti ih garantira ikakva vlada ili firma, što postavlja očito pitanje za svakog novog bitcoin ulagača: zašto imaju uopće ikakvu vrijednost? Za razliku od dionica, obveznica, nekretnina ili robe poput nafte i žita, bitcoine nije moguće vrednovati koristeći standardne ekonomske analize ili korisnost u proizvodnji drugih dobara. Bitcoini pripadaju sasvim drugoj kategoriji dobara - monetarnih dobara, čija se vrijednost definira kroz tzv. teoriju igara; svaki sudionik na tržištu vrednuje neko dobro, onoliko koliko procjenjuje da će ga drugi sudionici vrednovati. Kako bismo bolje razumjeli ovo svojstvo monetarnih dobara, trebamo istražiti podrijetlo novca.
Podrijetlo novca
U prvim ljudskim društvima, trgovina među grupama se vršila kroz robnu razmjenu. Velika neefikasnost prisutna u robnoj razmjeni je drastično ograničavala količinu i geografski prostor na kojem je bila moguća. Jedan od najvećih problema sa robnom razmjenom je problem dvostruke podudarnosti potražnje. Uzgajivač jabuka možda želi trgovati sa ribarom, ali ako ribar ne želi jabuke u istom trenutku, razmjena se neće dogoditi. Kroz vrijeme, ljudi su razvili želju za čuvanjem određenih predmeta zbog njihove rijetkosti i simbolične vrijednosti (npr. školjke, životinjski zube, kremen). Zaista, kako i Nick Szabo govori u svojem izvrsnom eseju o podrijetlu novca, ljudska želja za sakupljanjem predmeta pružila je izraženu evolucijsku prednost ranom čovjeku nad njegovim najbližim biološkim rivalom, neandertalcem - Homo neanderthalensis.
"Primarna i najbitnija evolucijska funkcija sakupljanja bila je osigurati medij za čuvanje i prenošenje vrijednosti".
Predmeti koje su ljudi sakupljali služili su kao svojevrsni “proto-novac,” tako što su omogućavale trgovinu među antagonističkim plemenima i dozvoljavale bogatsvu da se prenosi na sljedeću generaciju. Trgovina i transfer takvih predmeta bile su rijetke u paleolitskim društvima, te su oni služili više kao “spremište vrijednosti” (store of value) nego kao “medij razmjene” (medium of exchange), što je uloga koju danas igra moderni novac. Szabo objašnjava:
"U usporedbi sa modernim novcem, primitivan novac je imao jako malo “brzinu” - mogao je promijeniti ruke samo nekoliko puta u životu prosječnog čovjeka. Svejedno, trajni i čvrsti sakupljački predmet, što bismo danas nazvali “nasljeđe,” mogao je opstati mnogo generacija, dodajući znatnu vrijednost pri svakom transferu - i zapravo omogućiti transfer uopće".
Rani čovjek suočio se sa bitnom dilemom u teoriji igara, kada je odlučivao koje predmete sakupljati: koje od njih će drugi ljudi željeti? Onaj koji bi to točno predvidio imao bi ogromnu prednost u mogućnosti trgovine i akvizicije bogatsva. Neka američka indijanska plemena, npr. Naraganseti, specijalizirala su se u proizvodnji sakupljačkih dobara koja nisu imala drugu svrhu osim trgovine. Valja spomenuti da što je ranije predviđanje da će neko dobro imati takvu vrijednost, veća je prednost koju će imati onaj koji je posjeduje, zato što ju je moguće nabaviti jeftinije, prije nego postane vrlo tražena roba i njezona vrijednost naraste zajedno sa populacijom. Nadalje, nabava nekog dobra u nadi da će u budućnosti biti korišteno kao spremište vrijednosti, ubrzava upravo tu primjenu. Ova cirkularnost je zapravo povratna veza (feedback loop) koja potiče društva da se rapidno slože oko jednog spremišta vrijednosti. U terminima teorije igara, ovo je znano kao “Nashov ekvilibrij.” Postizanje Nashovog ekvilibrija za neko spremište vrijednosti je veliko postignuće za društvo, pošto ono znatno olakšava trgovinu i podjelu rada, i time omogućava napredak civilizacije.
Tisućljećima, kako su ljudska društva rasla i otvarala trgovinske puteve, različite aplikacije spremišta vrijednosti u individualnim društvima počele su se natjecati međusobno. Trgovci su imali izbor: čuvati svoju zaradu u spremištu vrijednosti vlastite kulture, ili one kulture sa kojom su trgovali, ili mješavini oboje. Benefit štednje u stranom spremištu vrijednosti bila je uvećana sposobnost trgovanja u povezanom stranom društvu. Trgovci koji su štedili u stranom spremištu vrijednosti su također imali dobrih razloga da potiču svoje društvo da ga prihvati, jer bi tako uvećali vrijednost vlastite ušteđevine. Prednosti “uvezene” tehnologije spremanja vrijednosti bile su prisutne ne samo za trgovce, nego i za sama društva. Kada bi se dvije grupe konvergirale u jedinstvenom spremištu vrijednosti, to bi značajno smanjilo cijenu troškova trgovine jednog s drugim, i samim time povećanje bogatstva kroz trgovinu. I zaista, 19. stoljeće bilo je prvi put da je najveći dio svijeta prihvatio jedinstveno spremište vrijednosti - zlato - i u tom periodu vidio najveću eksploziju trgovine u povijesti svijeta. O ovom mirnom periodu, pisao je John Maynard Keynes:
"Kakva nevjerojatna epizoda u ekonomskom napretku čovjeka… za svakog čovjeka iole iznadprosječnog, iz srednje ili više klase, život je nudio obilje, ugodu i mogućnosti, po niskoj cijeni i bez puno problema, više nego monarsima iz prethodnih perioda. Stanovnik Londona mogao je, ispijajući jutarnji čaj iz kreveta, telefonski naručiti razne proizvode iz cijele Zemlje, u količinama koje je želio, i sa dobrim razlogom očekivati njihovu dostavu na svoj kućni prag."
Svojstva dobrog spremišta vrijednosti
Kada se spremišta vrijednosti natječu jedno s drugim, specifična svojstva rade razliku koja daje jednom prednost nad drugim. Premda su mnoga dobra u prošlosti korištena kao spremišta vrijednosti ili kao “proto-novac,” određena svojstva su se pokazala kao posebno važna, i omogućila dobrima sa njima da pobijede. Idealno spremište vrijednosti biti će:
- Trajno: dobro ne smije biti kvarljivo ili lako uništeno. Tako naprimjer, žito nije idealno spremište vrijednosti.
- Prenosivo: dobro mora biti lako transportirati i čuvati, što omogućuje osiguranje protiv gubitka ili krađe i dopušta trgovinu na velike udaljenosti. Tako, krava je lošije spremište vrijednosti od zlatne narukvice.
- Zamjenjivo: jedna jedinica dobra treba biti zamjenjiva sa drugom. Bez zamjenjivosti, problem podudarnosti želja ostaje nerješiv. Time, zlato je bolje od dijamanata, jer su oni nepravilni u obliku i kvaliteti.
- Provjerljivo: dobro mora biti lako i brzo identificirano i testirano za autentičnost. Laka provjera povećava povjerenje u trgovini i vjerojatnost da će razmjena biti dovršena.
- Djeljivo: dobro mora biti lako djeljivo na manje dijelove. Premda je ovo svojstvo bilo manje važno u ranim društvima gdje je trgovina bila rijetka, postalo je važnije sa procvatom trgovine. Količine koje su se mijenjale postale su manje i preciznije.
- Oskudno: Monetarno dobro mora imati “cijenu nemoguću za lažirati,” kao što je rekao Nick Szabo. Drugim riječima, dobro ne smije biti obilno ili lako dostupno kroz proizvodnju. Oskudnost je možda i najvažnije svojstvo spremišta vrijednosti, pošto se izravno vezuje na ljudsku želju da sakupljamo ono što je rijetko. Ona je izvor vrijednosti u spremištu vrijednosti.
- Duge povijesti: što je dulje neko dobro vrijedno za društvo, veća je vjerojatnost da će biti prihvaćeno kao spremište vrijednosti. Dugo postojeće spremište vrijednosti biti će jako teško uklonjeno od strane došljaka, osim u slučaju sile (ratno osvajanje) ili ako je nova tehnologija znatno bolja u ostalim svojstvima.
- Otporno na cenzuru: novije svojstvo, sve više važno u modernom digitalnom svijetu sa sveprisutnim nadzorom, je otpornost na cenzuru. Drugim riječima, koliko je teško da vanjski agent, kao korporacija ili država, spriječi vlasnika dobra da ga čuva i koristi. Dobra koja su otporna na cenzuru su idealna za ljude koji žive u režimima koji prisilno nadziru kapital ili čine neke oblike mirne trgovine protuzakonitima.
Ova tablica ocjenjuje Bitcoin, zlato (gold) i fiat novac (kao što je euro ili dolar) po svojstvima izlistanim gore. Objašnjenje svake ocjene slijedi nakon tablice.
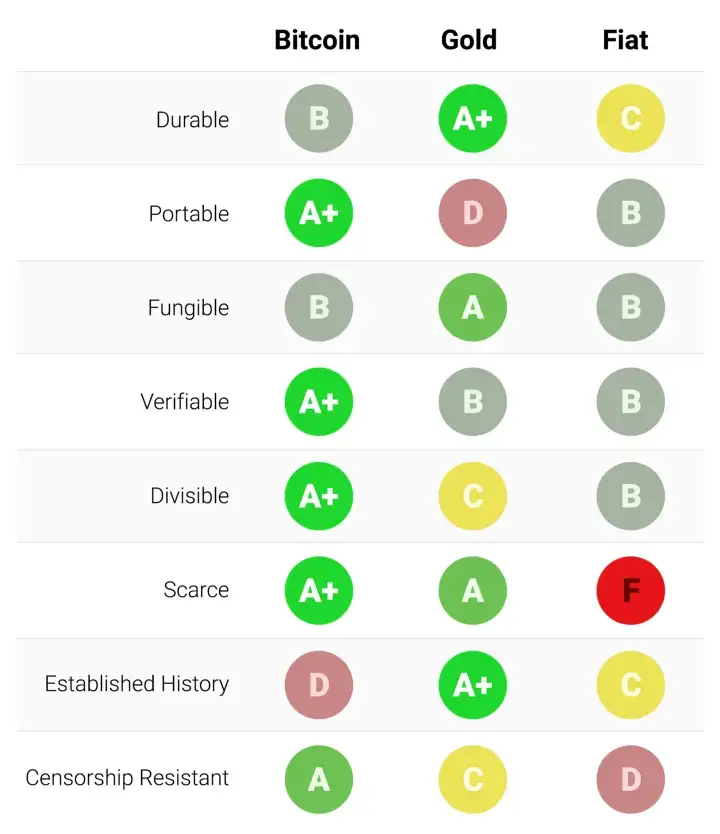
Trajnost:
Zlato je neosporeni kralj trajnosti. Velika većina zlata pronađenog kroz povijest, uključujući ono egipatskih faraona, opstaje i danas i vjerojatno će postojati i za tisuću godina. Zlatnici korišteni u antičko doba imaju značajnu vrijednost i danas. Fiat valute i bitcoini su digitalni zapisi koji ponekad imaju fizički oblik (npr. novčanice). Dakle, njihovu trajnost ne određuju njihova fizička svojstva (moguće je zamijeniti staru i oštećenu novčanicu za novu), nego institucije koje stoje iza njih. U slučaju fiat valuta, mnoge države su nastale i nestale kroz stoljeća, i valute su nestale s njima. Marke iz Weimarske republike danas nemaju vrijednost zato što institucija koja ih je izdavala više ne postoji. Ako je povijest ikakav pokazatelj, ne bi bilo mudro smatrati fiat valute trajnima dugoročno; američki dolar i britanska funta su relativne anomalije u ovom pogledu. Bitcoini, zato što nemaju instituciju koja ih održava, mogu se smatrati trajnima dok god mreža koja ih osigurava postoji. Obzirom da je Bitcoin još uvijek mlada valuta, prerano je za čvrste zaključke o njegovoj trajnosti. No, postoje ohrabrujući znakovi - prominente države su ga pokušavale regulirati, hakeri ga napadali - usprkos tome, mreža nastavlja funkcionirati, pokazujući visok stupanj antifragilnosti.
Prenosivost:
Bitcoini su najprenosivije spremište vrijednosti ikad. Privatni ključevi koji predstavljaju stotine milijuna dolara mogu se spremiti na USB drive i lako ponijeti bilo gdje. Nadalje, jednako velike sume mogu se poslati na drugi kraj svijeta skoro instantno. Fiat valute, zbog svojeg temeljno digitalnog oblika, su također lako prenosive. Ali, regulacije i kontrola kapitala od strane države mogu ugroziti velike prijenose vrijednosti, ili ih usporiti danima. Gotovina se može koristiti kako bi se izbjegle kontrole kapitala, ali onda rastu rizik čuvanja i cijena transporta. Zlato, zbog svojeg fizičkog oblika i velike gustoće, je najmanje prenosivo. Nije čudo da većina zlatnika i poluga nikad ne napuste sefove. Kada se radi prijenos zlata između prodavača i kupca, uglavnom se prenosi samo ugovor o vlasništvu, ne samo fizičko zlato. Prijenos fizičkog zlata na velike udaljenosti je skupo, riskantno i sporo.
Zamjenjivost:
Zlato nam daje standard za zamjenjivost. Kada je rastopljeno, gram zlata je praktički nemoguće razlikovati od bilo kojeg drugog grama, i zlato je oduvijek bilo takvo. S druge strane, fiat valute, su zamjenjive samo onoliko koliko njihova institucija želi da budu. Iako je uglavnom slučaj da je novčanica zamjenjiva za drugu istog iznosa, postoje situacije u kojima su velike novčanice tretirane drukčije od malih. Naprimjer, vlada Indije je, u pokušaju da uništi neoporezivo sivo tržište, potpuno oduzela vrijednost novčanicama od 500 i 1000 rupija. To je uzrokovalo da ljudi manje vrednuju te novčanice u trgovini, što je značilo da više nisu bile zaista zamjenjive za manje novčanice. Bitcoini su zamjenjivi na razini mreže; svaki bitcoin je pri prijenosu tretiran kao svaki drugi. No, zato što je moguće pratiti individualne bitcoine na blockchainu, određeni bitcoin može, u teoriji, postati “prljav” zbog korštenja u ilegalnoj trgovini, te ga trgovci ili mjenjačnice možda neće htjeti prihvatiti. Bez dodatnih poboljšanja oko privatnosti i anonimnosti na razini mrežnog protokola, bitcoine ne možemo smatrati jednako zamjenjivim kao zlato.
Mogućnost provjere:
Praktično gledajući, autentičnost fiat valuta i zlata je prilično lako provjeriti. Svejedno, i usprkos pokušajima da spriječe krivotvorenje novčanica, i dalje postoji potencijal prevare za vlade i njihove građane. Zlato također nije imuno na krivotvorenje. Sofisticirani kriminalci su koristili pozlaćeni tungsten kako bi prevarili kupce zlata. Bitcoine je moguće provjeriti sa matematičkom sigurnošću. Korištenjem kriptografskih potpisa, vlasnik bitcoina može javno demonstrirati da posjeduje bitcoine koje tvrdi da posjeduje.
Djeljivost:
Bitcoine je moguće podijeliti u stotinu milijuna manjih jedinica (zvanih satoshi), i prenositi takve (no, valja uzeti u obzir ekonomičnost prijenosa malih iznosa, zbog cijene osiguravanja mreže - “network fee”). Fiat valute su tipično dovoljno djeljive na jedinice sa vrlo niskom kupovnom moći. Zlato, iako fizički i teoretski djeljivo, postaje teško za korištenje kada se podijeli na dovoljno male količine da bi se moglo koristiti u svakodnevnoj trgovini.
Oskudnost:
Svojstvo koje najjasnije razlikuje Bitcoin od fiat valuta i zlata je njegova unaprijed definirana oskudnost. Od početka, konačna količina bitcoina nikad neće biti veća od 21 milijun. To daje vlasnicima bitcoina jasan i znan uvid u postotak ukupnog vlasništva. Naprimjer, vlasnik 10 bitcoina bi znao da najviše 2,1 milijuna ljudi (manje od 0.03% populacije) može ikad imati isto bitcoina kao i on. Premda je kroz povijest uvijek bilo oskudno, zlato nije imuno na povećanje ukupne količine. Ako se ikad izumi nova, ekonomičnija metoda rudarenja ili proizvodnje zlata, ukupna količina zlata bi se mogla dramatično povećati (npr. rudarenje morskog dna ili asteroida). Na kraju, fiat valute, relativno nov izum u povijesti, pokazale su se sklonima konstantnim povećanjima u količini. Države su pokazale stalnu sklonost inflaciji monetarne kvantitete kako bi rješavale kratkoročne političke probleme. Inflacijske tendencije vlada diljem svijeta čine fiat valute gotovo sigurnim da će gubiti vrijednost kroz vrijeme.
Etablirana povijest:
Nijedno monetarno dobro nema povijest kao zlato, koje je imalo vrijednost za cijelog trajanja ljudske civilizacije. Kovanice izrađene u antičko doba i danas imaju značajnu vrijednost. Ne može se isto reći za fiat valute, koje su same relativno nova povijesna anomalija. Od njihovog početka, fiat valute su imale gotovo univerzalni smjer prema bezvrijednosti. Korištenje inflacije kao podmuklog načina za nevidljivo oporezivanje građana je vječita kušnja kojoj se skoro nijedna država u povijesti nije mogla oduprijeti. Ako je 20. stoljeće, u kojem je fiat novac dominirao globalni monetarni poredak, demonstriralo neku ekonomsku istinu, to je onda bila ta da ne možemo računati na fiat novac da održi vrijednost u dužem ili srednjem vremenskom periodu. Bitcoin, usprkos svojoj novosti, je preživio dovoljno testova tržišta da postoji velika vjerojatnost da neće nestati kao vrijedno dobro. Nadalje, Lindy efekt govori da što duže Bitcoin bude korišten, to će veća biti vjera u njega i njegovu sposobnost da nastavi postojati dugo u budućnost. Drugim riječima, društvena vjera u monetarno dobro je asimptotička, kao u grafu ispod:
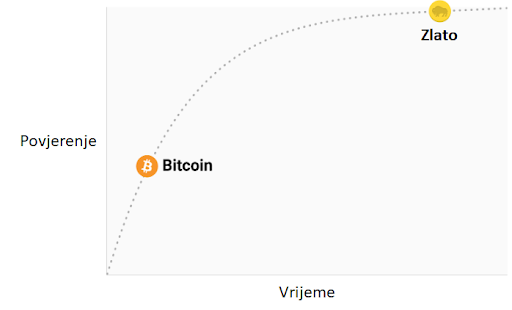
Ako Bitcoin preživi prvih 20 godina, imat će gotovo sveopće povjerenje da će trajati zauvijek, kao što ljudi vjeruju da je internet trajna stvar u modernom svijetu.
Otpor na cenzuru
Jedan od najbitnijih izvora za ranu potražnju bitcoina bila je njegova upotreba u ilegalnoj kupovini i prodaji droge. Mnogi su zato pogrešno zaključili da je primarna potražnja za bitcoinima utemeljena u njihovoj prividnoj anonimnosti. Međutim, Bitcoin nije anonimna valuta; svaka transakcija na mreži je zauvijek zapisana na javnom blockchainu. Povijesni zapis transakcija dozvoljava forenzičkoj analizi da identificira izvore i tijek sredstava. Takva analiza dovela je do uhićenja počinitelja zloglasne MtGox pljačke. Premda je istina da dovoljno oprezna i pedantna osoba može sakriti svoj identitet koristeći Bitcoin, to nije razlog zašto je Bitcoin bio toliko popularan u trgovini drogom.
Ključno svojstvo koje čini Bitcoin najboljim za takve aktivnosti je njegova agnostičnost i nepotrebnost za dozvolom (“premissionlessness”) na mrežnoj razini. Kada se bitcoini prenose na Bitcoin mreži, ne postoji nitko tko dopušta transakcije. Bitcoin je distribuirana peer-to-peer (korisnik-korisniku) mreža, i samim time dizajnirana da bude otporna na cenzuru. Ovo je u velikom kontrastu sa fiat bankarskim sustavom, u kojem države reguliraju banke i ostale institucije prijenosa novca, kako bi one prijavljivale i sprječavale protuzakonito korištenje monetarnih dobara. Klasičan primjer regulacije novca su kontrole kapitala. Npr., bogati milijunaš će vrlo teško prenijeti svoje bogatstvo u novu zemlju, kada bježi iz opresivnog režima. Premda zlato nije izdano i proizvedeno od države, njegova fizička priroda ga čini teško prenosivim kroz prostor, i samim time ga je daleko lakše regulirati nego Bitcoin. Indijski Akt kontrole zlata je primjer takve regulacije.
Bitcoin je odličan u većini gore navedenih svojstava, što mu omogućava da bude marginalno bolji od modernih i drevnih monetarnih dobara, te da pruži poticaje za svoje rastuće društveno usvajanje. Specifično, moćna kombinacija otpornosti na cenzuru i apsolutne oskudnosti bila je velika motivacija za bogate ulagače koji su uložili dio svojeg bogatstva u Bitcoin.
Evolucija novca
U modernoj monetarnoj ekonomiji postoji opsesija sa ulogom novca kao medija razmjene. U 20. stoljeću, države su monopolizirale izdavanje i kontrolu novca i kontinuirano potkopavale njegovo svojstvo spremišta vrijednosti, stvarajući lažno uvjerenje da je primarna svrha novca biti medij razmjene. Mnogi su kritizirali Bitcoin, govoreći da je neprikladan da bude novac zato što mu je cijena bila previše volatilna za medij razmjene. No, novac je uvijek evoluirao kroz etape; uloga spremišta vrijednosti je dolazila prije medija razmjene. Jedan od očeva marginalističke ekonomije, William Stanley Jevons, objašnjava:
"Povijesno govoreći… čini se da je zlato prvo služilo kao luksuzni metal za ukras; drugo, kao sačuvana vrijednost; treće, kao medij razmjene; i konačno, kao mjerilo vrijednosti."
U modernoj terminologiji, novac uvijek evoluira kroz četiri stadija:
- Kolekcionarstvo: U prvoj fazi svoje evolucije, novac je tražen samo zbog svojih posebnih svojstava, uglavnom zbog želja onog koji ga posjeduje. Školjke, perlice i zlato su bili sakupljani prije nego su poprimili poznatije uloge novca.
- Spremište vrijednosti: Jednom kada je novac tražen od dovoljnog broja ljudi, biti će prepoznat kao način za čuvanje i spremanje vrijednosti kroz vrijeme. Kada neko dobro postane široko korišteno kao spremište vrijednosti, njegova kupovna moć raste sa povećanom potražnjom za tu svrhu. Kupovna moć spremišta vrijednosti će u jednom trenutku doći do vrhunca, kada je dovolno rašireno i broj novih ljudi koji ga potražuju splasne.
- Sredstvo razmjene: Kada je novac potpuno etabliran kao spremište vrijednosti, njegova kupovna moć se stabilizira. Nakon toga, postane prikladno sredstvo razmjene zbog stabilnosti svoje cijene. U najranijim danima Bitcoina, mnogi ljudi nisu shvaćali koju buduću cijenu plaćaju koristeći bitcoine kao sredstvo razmjene, umjesto kao novonastalo spremište vrijednosti. Poznata priča o čovjeku koji je za 10,000 bitcoina (vrijednih oko 94 milijuna dolara kada je ovaj članak napisan) za dvije pizze ilustrira ovaj problem.
- Jedinica računanja vrijednosti: Jednom kada je novac široko korišten kao sredstvo razmjene, dobra će biti vrednovana u njemu, tj. većina cijena će biti izražena u njemu. Uobičajena zabluda je da je većinu dobara moguće zamijeniti za bitcoine danas. Npr., premda je možda moguće kupiti šalicu kave za bitcoine, izlistana cijena nije prava bitcoin cijena; zapravo se radi o cijeni u državnoj valuti koju želi trgovac, preračunatu u bitcoin po trenutnoj tržišnoj cijeni. Kad bi cijena bitcoina pala u odnosu na valutu, vrijednost šalice izražena u bitcoinima bi se povećala. Od trenutka kada trgovci budu voljni prihvaćani bitcoine kao platežno sredstvo, bez obraćanja pažnje na vrijednost bitcoina u državnoj fiat valuti, moći ćemo reći da je Bitcoin zaista postao jedinica računanja vrijednosti.
Monetarna dobra koja još nisu jedinice računanja vrijednosti možemo smatrati “djelomično monetiziranima.” Danas zlato ima takvu ulogu, jer je spremište vrijednosti, ali su mu uloge sredstva razmjene i računanja vrijednosti oduzete intervencijama država. Moguće je također da se jedno dobro koristi kao sredstvo razmjene, dok druga ispunjavaju ostale uloge. To je tipično u zemljama gdje je država disfunkcionalna, npr. Argentina ili Zimbabwe. U svojoj knjizi, Digitalno zlato, Nathaniel Popper piše:
"U Americi, dolar služi trima funkcijama novca: nudi sredstvo razmjene, jedinicu za mjerenje vrijednosti dobara, i mjesto gdje se može čuvati vrijednosti. S druge strane, argentinski peso je korišten kao sredstvo razmjene (za svakodnevne potrebe), ali ga nitko nije koristio kao spremište vrijednosti. Štednja u pesosima bila je ekvivalent bacanja novca. Zato su ljudi svu svoju štednju imali u dolarima, jer je dolar bolje čuvao vrijednost. Zbog volatilnosti pesosa, ljudi su računali cijene u dolarima, što im je pružalo pouzdaniju jedinicu mjerenja kroz vrijeme."
Bitcoin je trenutno u fazi tranzicije iz prvog stadija monetizacije u drugi. Vjerojatno će proći nekoliko godina prije nego Bitcoin pređe iz začetaka spremišta vrijednosti u istinski medij razmjene, i put do tog trenutka je još uvijek pun rizika i nesigurnosti. Važno je napomenuti da je ista tranzicija trajala mnogo stoljeća za zlato. Nitko danas živ nije doživio monetizaciju dobra u realnom vremenu (kroz koju Bitcoin prolazi), tako da nemamo puno iskustva govoriti o putu i načinu na koji će se monetizacija dogoditi.
Put monetizacije
Kroz proces monetizacije, monetarno dobro će naglo porasti u kupovnoj moći. Mnogi su tako komentirali da je uvećanje kupovne moći Bitcoina izgledalo kao “balon” (bubble). Premda je ovaj termin često korišten kako bi ukazao na pretjeranu vrijednosti Bitcoina, sasvim slučajno je prikladan. Svojstvo koje je uobičajeno za sva monetarna dobra jest da je njihova kupovna moć viša nego što se može opravdati samo kroz njihovu uporabnu vrijednost. Zaista, mnogi povijesni novci nisu imali uporabnu vrijednost. Razliku između kupovne moći i vrijednosti razmjene koju bi novac mogao imati za svoju inherentnu korisnost, možemo razmatrati kao “monetarnu premiju.” Kako monetarno dobro prolazi kroz stadije monetizacije (navedene gore), monetarna premija raste. No, ta premija ne raste u ravnoj i predvidivoj liniji. Dobro X, koje je bilo u procesu monetizacije, može izgubiti u usporedbi sa dobrom Y koje ima više svojstava novca, te monetarna premija dobra X drastično padne ili potpuno nestane. Monetarna premija srebra je skoro potpuno nestala u kasnom 19. stoljeću, kada su ga vlade diljem svijeta zamijenile zlatom kao novcem.
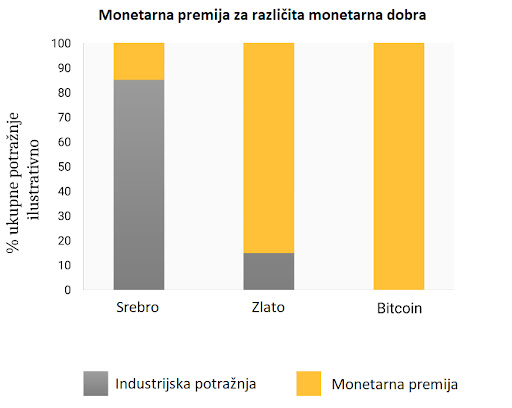
Čak i u odsustvu vanjskih faktora, kao što su intervencije vlade ili druga monetarna dobra, monetarna premija novog novca neće ići predvidivim putem. Ekonomist Larry White primijetio je:
"problem sa pričom “balona,” naravno, je da je ona konzistentna sa svakim putem cijene, i time ne daje ikakvo objašnjenje za specifičan put cijene"
Proces monetizacije opisuje teorija igara; svaki akter na tržištu pokušava predvidjeti agregiranu potražnju ostalih aktera, i time buduću monetarnu premiju. Zato što je monetarna premija nevezana za inherentnu korisnost, tržišni akteri se uglavnom vode za prošlim cijenama da bi odredili je li neko dobro jeftino ili skupo, i žele li ga kupiti ili prodati. Veza trenutne potražnje sa prošlim cijenama naziva se “ovisnost o putu” (path dependence); ona je možda najveći izvor konfuzije u shvaćanju kretanja cijena monetarnih dobara.
Kada kupovna moć monetarnog dobra naraste zbog većeg i šireg korištenja, očekivanja tržišta o definicijama “jeftinog” i “skupog” se mijenjaju u skladu s time. Slično tome, kada cijena monetarnog dobra padne, očekivanja tržišta mogu se promijeniti u opće vjerovanje da su prethodne cijene bile “iracionalne” ili prenapuhane. Ovisnost o putu novca ilustrirana je riječima poznatog upravitelja fondova s Wall Streeta, Josha Browna:
"Kupio sam bitcoine kada su koštali $2300, i to mi se udvostručilo gotovo odmah. Onda sam počeo govoriti kako “ne mogu kupiti još” dok im je cijena rasla, premda sam znao da je to razmišljanje bazirano samo na cijenu po kojoj sam ih kupio. Kasnije, kada je cijena pala zbog kineske regulacije mjenjačnica, počeo sam si govoriti, “Odlično, nadam se da će još pasti da mogu kupiti još.”"
Istina leži u tome da su ideje “jeftinog” i “skupog” zapravo besmislene kada govorimo o monetarnim dobrima. Cijena monetarnog dobra ne reflektira njegovu stopu rasprostanjenosti ili korisnosti, nego mjeru koliko je ono široko prihvaćeno da ispuni razne uloge novca.
Dodatna komplikacija u ovom aspektu novca je činjenica da tržišni akteri ne djeluju samo kao nepristrani promatrači koji pokušavaju kupiti i prodati u iščekivanju budućih kretanja monetarne premije, nego i kao aktivni proponenti. Pošto ne postoji objektivno “točna” monetarna premija, širiti dobar glas o superiornijim svojstvima nekog monetarnog dobra je efektivnije nego za obična dobra, čija vrijednost je u konačnici vezana na njegovu osnovnu korisnost. Religiozni zanos sudionika na Bitcoin tržištu vidljiv je na raznim internetskim forumima, gdje Bitcoineri aktivno promoviraju benefine Bitcoina i bogatstvo koje je moguće ostvariti investiranjem u njega. Promatrajući Bitcoin tržište, Leigh Drogen komentira:
"To je prepoznatljivo svima kao religija - priča koju si pričamo i oko koje se slažemo. Religija je krivulja na grafu prihvaćanja o kojoj trebamo razmišljati. Sustav je gotovo savršen - onog trenutka kada netko pristupi krugu Bitcoinera, to će reći svima i nastaviti širiti riječ. Onda njihovi prijatelji pristupe i nastave širiti riječ."
Premda usporedba sa religijom može staviti Bitcoin u iracionalno svjetlo, potpuno je racionalno za individualnog vlasnika da širi dobru vijest o superiornom monetarnom dobru, i za šire društvo da se standardizira oko njega. Novac djeluje kao temelj za svu trgovinu i štednju; tako da prihvaćanje superiornog oblika novca ima ogromne multiplicirajuće benefite za stvaranje bogatstva za sve članove društva.
Oblik monetizacije
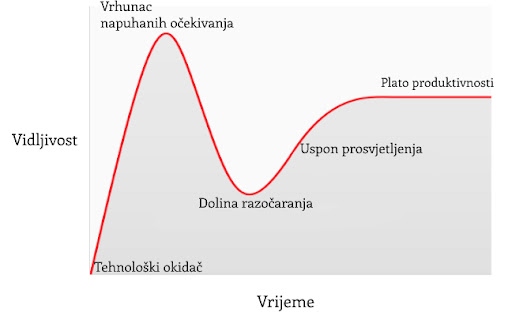
U članku o Spekulativnom prihvaćanju Bitcoina / teorije cijene, Michael Casey postulira da rastući Gartner hype ciklusi predstavljaju faze standardne S-krivulje prihvaćanja novih tehnologija, koje su bile prisutne kod mnogih transformacijskih tehnologija dok su postajale uobičajene u društvu.
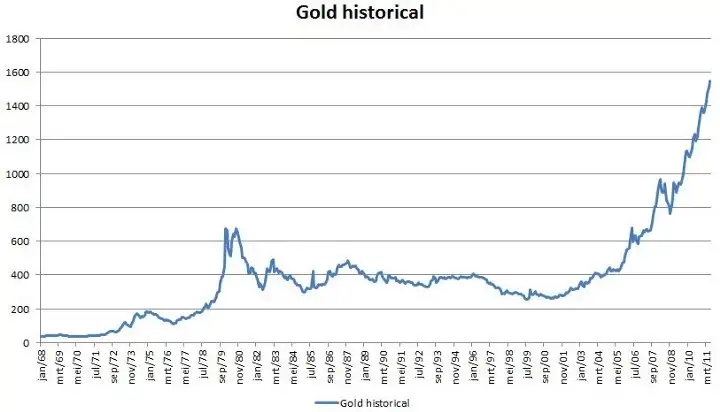
Svaki Gartner hype ciklus počinje sa eksplozijom entuzijazma za novom tehnologijom, a cijenu podižu oni sudionici na tržištvu koji su “dostupni” u toj fazi. Najraniji kupci u Gartner hype ciklusu obično imaju jaku vjeru o transformacijskoj prirodi tehnologije u koju ulažu. S vremenom, tržište dosegne vrhunac entuzijazma kako se količina novih kupaca iscrpljuje, te kupovinom počnu dominirati spekulatori koji su više zainteresirani u brze profite nego u samu tehnologiju.
Nakon vrha hype ciklusa, cijene rapidno padaju dok spekulativno ludilo ustupa mjesto očajavanju, javnoj poruzi i osjećaju da tehnologija nije uopće bila transformacijska. S vremenom, cijena dosegne dno i formira plato na kojem se originalnim ulagačima, koji su imali snažno uvjerenje, pridružuju nove grupe ljudi koji su izdržali bol kraha cijena i koji cijene važnost same tehnologije.
Plato traje neko vrijeme i formira, kako Casey kaže, “stabilnu, dosadnu dolinu.” Za ovo vrijeme, javni interes za tehnologiju opada, no nastaviti će se razvijati i snažna zajednica uvjerenja će polako rasti. Tada, postavlja se nova baza za sljedeću iteraciju hype ciklusa, dok vanjski promatrači prepoznaju da tehnologija i dalje postoji i da ulaganje u nju možda nije onoliko rizično kao što se činilo za vrijeme pada cijene. Sljedeća iteracija hype ciklusa donosi mnogo veći broj novih ljudi, pa je i ciklus daleko veći u svojoj magnitudi.
Jako mali broj ljudi koji sudjeluju u Gartner hype ciklusu će točno predvidjeti koliko će visoko cijena porasti za vrijeme ciklusa. Cijene često dosegnu razine koje bi se činile apsurdnima većini ulagača u raniji stadijima ciklusa. Kada ciklus završi, mediji tipično atribuiraju pad cijene nekoj od aktualnih drušvenih tema. Premda takva tema može biti okidač pada, ona nikad nije temeljni razlog zašto ciklus završava. Gartner hype ciklusi završavaju kada je količina dostupnih novih sudionika na tržištu iscrpljena.
Zanimljivo je da je i zlato nacrtalo klasičan graf Gartner hype ciklusa od kasnih 1970-ih do ranih 2000-ih. Moguće je spekulirati da je hype ciklus osnovna socijalna dinamika oko procesa monetizacije.
Gartner kohorte
Od početka trgovanja Bitcoina na mjenjačnicama 2010. godine, Bitcoin tržište je svjedočilo četirima velikim Gartner hype ciklusima. U retrospektivi, možemo vrlo precizno identificirati grupe cijena prethodnih hype ciklusa Bitcoin tržišta. Također, možemo kvalitativno odrediti kohorte ulagača koje su povezane sa svakom iteracijom prethodnih ciklusa.
$ 0–$ 1 (2009. – 3. mjesec 2011.): Prvi hype ciklus u Bitcoin tržištu dominirali su kriptografi, računalni znanstvenici i cypherpunkovi koji su od početka bili spremni razumijeti važnost nevjerojatnog izuma Satoshija Nakamotoa, i koji su bili pioniri u potvrđivanju da Bitcoin protokol nema tehničkih mana.
$ 1–$ 30 (3. mjesec 2011. – 7. mjesec. 2011.): Drugi ciklus privukao je rane entuzijaste oko novih tehnologija kao i stabilan pritok ideološki motiviranih ulagača koji su bili oduševljeni idejom novca odvojenog od države. Libertarijanci poput Rogera Vera došli su u Bitcoin zbog aktivnog anti-institucionalnog stava, i mogućnosti koju je nova tehnologija obećavala. Wences Casares, briljantni i dobro povezani serijski poduzetnik, bio je također dio drugog Bitcoin hype ciklusa te je širio riječ o Bitcoinu među najprominentnijim tehnolozima i ulagačima u Silicijskoj Dolini.
$ 250–$ 1100 (4. mjesec 2013. – 12. mjesec 2013.): Treći hype ciklus doživio je ulazak ranih generalnih i institucionalnih ulagača koji su bili voljni uložiti trud i riskirati kroz užasno komplicirane kanale likvidnosti kako bi kupili bitcoine. Primaran izvor likvidnosti na tržištu za vrijeme ovog perioda bio je MtGox, mjenjačnica bazirana u Japanu, koju je vodio notorno nesposobni i beskrupulozni Mark Karpeles, koji je kasnije završio i u zatvoru zbog svoje uloge u kolapsu MtGoxa.
Valja primijetiti da je rast Bitcoinove cijene za vrijeme spomenuti hype ciklusa većinom povezano sa povećanjem likvidnosti i lakoćom sa kojom su ulagači mogli kupiti bitcoine. Za vrijeme prvog hype ciklusa, nisu postojale mjenjačnice; akvizicija bitcoina se odvijala primarno kroz rudarenje (mining) ili kroz izravnu razmjenu sa onima koju su već izrudarili bitcoine. Za vrijeme drugog hype ciklusa, pojavile su se rudimentarne mjenjačnice, no nabavljanje i osiguravanje bitcoina na ovim mjenjačnicama bilo je previše kompleksno za sve osim tehnološki najsposobnijih ulagača. Čak i za vrijeme trećeg hype ciklusa, ulagači koju su slali novac na MtGox kako bi kupili bitcoine su morali raditi kroz značajne prepreke. Banke nisu bile voljne imati posla sa mjenjačnicom, a oni posrednici koji su nudili usluge transfera bili su često nesposobni, kriminalni, ili oboje. Nadalje, mnogi koji su uspjeli poslati novac MtGoxu, u konačnici su morali prihvatiti gubitak svojih sredstava kada je mjenjačnica hakirana i kasnije zatvorena.
Tek nakon kolapsa MtGox mjenjačnice i dvogodišnje pauze u tržišnoj cijeni Bitcoina, razvili su se zreli i duboki izvori likvidnosti; primjeri poput reguliranih mjenjačnica kao što su GDAX i OTC brokeri kao Cumberland mining. Dok je četvrti hype ciklus započeo 2016. godine, bilo je relativno lako običnim ulagačima kupiti i osigurati bitcoine.
$ 1100 – $ 19600? (2014. –?):
U trenutku pisanja ovog teksta, tržište Bitcoina je prolazilo svoj četvrti veliki hype ciklus. Sudjelovanje u ovom hype ciklusu dominirala je ona skupina koju je Michael Casey opisao kao “rana većina” običnih i institucionalnih ulagača.
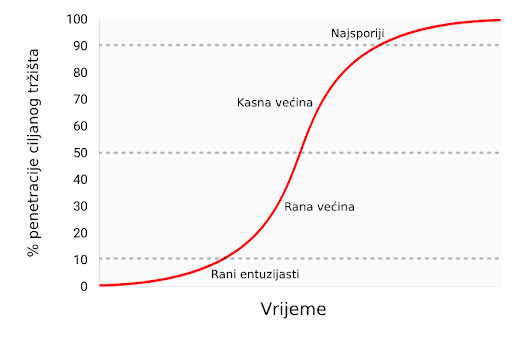
Kako su se izvori likvidnosti produbljivali i sazrijevali, veliki institucionalni ulagači sada imaju priliku sudjelovati kroz regulirana “futures” tržišta. Dostupnosti takvih tržišta stvara put ka kreaciji Bitcoin ETF-a (exchange traded fund) (fond na slobodnom tržištu), koji će onda pokrenuti “kasnu većinu” i “najsporije” u sljedećim hype ciklusima.
Premda je nemoguće predvidjeti točan efekt budućih hype ciklusa, razumno je očekivati da će najviša točka biti između $ 20.000 i $ 50.000 (2021. zenit je bio preko $ 69.000). Znatno više od ovog raspona, i Bitcoin bi imao znatan postotak ukupne vijednosti zlata (zlato i Bitcoin bi imali jednaku tržišnu kapitalizaciju kada bi bitcoini vrijedili oko $ 380.000 u trenutku pisanja ovog teksta). Značajan postotak vrijednosti zlata dolazi od potražnje centralnih banaka, te je malo vjerojatno da će centralne banke ili suverene države sudjelovati u trenutnom hype ciklusu.
Ulazak suverenih država u Bitcoin
Bitcoinov zadnji Gartner hype ciklus će započeti kada ga suverene države počnu akumulirati kao dio svojih rezervi stranih valuta. Tržišna kapitalizacija Bitcoina je trenutno premala da bismo ga smatrali značajnim dodatkom rezervama većini zemalja. No, kako se interes u privatnom sektoru povećava i kapitalizacija Bitcoina se približi trilijunu dolara, postat će dovoljno likvidan za većinu država. Prva država koja službeno doda bitcoine u svoje rezerve će vjerojatno potaknuti stampedo ostalih da učine isto. Države koje su među prvima u usvajanju Bitcoina imat će najviše benefita u svojim knjigama ako Bitcoin u konačnici postane globalna valuta (global reserve currency). Nažalost, vjerojatno će države sa najjačom izvršnom vlasti - diktature poput Sjeverne Koreje - biti najbrže u akumulaciji bitcoina. Neodobravanje prema takvim državama i slaba izvršna tijela zapadnjačkih demokracija uzrokovat će sporost i kašnjenje u akumulaciji bitcoina za njihove vlastite rezerve.
Velika je ironija u tome što je SAD trenutno jedna od regulatorno najotvorenijih nacija prema Bitcoinu, dok su Kina i Rusija najzatvorenije. SAD riskira najviše, geopolitički, ako bi Bitcoin zamijenio dolar kao svjetska rezervna valuta. U 1960-ima, Charles de Gaulle je kritizirao “pretjeranu privilegiju” (“exorbitant privilege”) koju su SAD imale u međunarodnom monetarnom poretku, postavljenom kroz Bretton Woods dogovor 1944. godine. Ruska i kineska vlada još ne shvaćaju geo-strateške benefite Bitcoina kao rezervne valute, te se trenutno brinu o efektima koje bi mogao imati na njihova unutarnja tržišta. Kao de Gaulle u 1960-ima, koji je prijetio SAD-u povratkom na klasični standard zlata, Kinezi i Rusi će s vremenom uvidjeti korist u velikoj poziciji u Bitcoinu - spremištu vrijednosti bez pokrića ijedne vlade. Sa najvećom koncentracijom rudara Bitcoina u Kini (2017.), kineska vlada već ima znatnu potencijalnu prednost u stavljanju bitcoina u svoje rezerve.
SAD se ponosi svojim statusom nacije inovatora, sa Silicijskom dolinom kao krunom svoje ekonomije. Dosad, Silicijska dolina je dominirala konverzacijom usmjerenom prema regulaciji, i poziciji koju bi ona treba zauzeti prema Bitcoinu. No, bankovna industrija i federalna rezerva SAD-a (US Federal Reserve, Fed) napokon počinju uviđati egzistencijalnu prijetnju koju Bitcoin predstavlja za američku monetarnu politiku, postankom globalne rezervne valute. Wall Street Journal, jedan od medijskih glasova federalne reserve, izdao je komentar o Bitcoinu kao prijetnji monetarnoj politici SAD-a:
"Postoji još jedna opasnost, možda i ozbiljnija iz perspektive centralnih banaka i regulatora: bitcoin možda ne propadne. Ako je spekulativni žar u kriptovalutu samo prvi pokazatelj njezinog šireg korištenja kao alternative dolaru, Bitcoin će svakako ugroziti monopol centralnih banaka nad novcem."
U narednim godinama, možemo očekivati veliku borbu između poduzetnika i inovatora u Silicijskoj dolini, koji će pokušavati čuvati Bitcoin od državne kontrole s jedne strane, i bankovne industrije i centralnih banaka koje će učiniti sve što mogu da bi regulirale Bitcoin kako bi spriječile znatne promjene u svojoj industriji i moći izdavanja novca, s druge.
Prijelaz na medij razmjene
Monetarno dobro ne može postati opće prihvaćen medij razmjene (standardna ekonomska definicija za “novac”) prije nego je vrednovano od širokog spektra ljudi; jednostavno, dobro koje nije vrednovano neće biti prihvaćeno u razmjeni. Kroz proces generalnog rasta vrijednosti, i time postanka spremišta vrijednosti, monetarno dobro će brzo narasti u kupovnoj moći, i time stvoriti cijenu za korištenje u razmjeni. Samo kada ta cijena rizika mijenjanja spremišta vrijednosti padne dovoljno nisko, može dobro postati opće prihvaćen medij razmjene.
Preciznije, monetarno dobro će biti prikladno kao medij razmjene samo kada je suma cijene rizika i transakcijske cijene u razmjeni manja nego u trgovini bez tog dobra.
U društvu koje vrši robnu razmjenu, prijelaz spremišta vrijednosti u medij razmjene može se dogoditi čak i onda kada monetarno dobro raste u kupovnoj moći, zato što su transakcijski troškovi robne razmjene iznimno visoki. U razvijenoj ekonomiji, u kojoj su troškovi razmjene niski, moguće je za mladu i rapidno rastućnu tehnologiju spremišta vrijednosti, poput Bitcoina, da se koristi kao medij razmjene, doduše na ograničen način. Jedan primjer je ilegalno tržište droge, gdje su kupci voljni žrtvovati oportunu cijenu čuvanja bitcoina kako bi umanjili znatan rizik kupovine droge koristeći fiat novac.
Postoje međutim velike institucionalne barijere da novonastalo spremište vrijednosti postane sveopće prihvaćen medij razmjene u razvijenom društvu. Države koriste oporezivanje kao moćnu metodu zaštite svojeg suverenog novca protiv rivalskih monetarnih dobara. Ne samo da suvereni novac ima prednost konstantnog izvora potražnje, zato što je porez moguće platiti jedino u njemu, nego su i rivalska monetarna dobra oporezana pri svakoj razmjeni za vrijeme rastuće cijene. Ova metoda oporezivanja stvara znatan otpor korištenju spremišta vrijednosti kao medija razmjene.
Ovakvo sabotiranje tržišnih monetarnih dobara nije nepremostiva barijera za njihovo prihvaćanje kao općeg medija razmjene. Ako ljudi izgube vjeru u suvereni novac, njegova vrijednost može rapidno propasti kroz proces zvan hiperinflacija. Kada suvereni novac prolazi kroz hiperinflaciju, njegova vrijednost propadne prvo u usporedbi sa najlikvidnijim dobrima u društvu, kao što je zlato ili stabilna strana valuta (američki dolar npr.), ako su ona dostupna. Kada nema likvidnih dobara ili ih ima premalo, novac u hiperinflaciji kolabira u usporedbi sa stvarnim dobrima, kao što su nekretnine ili upotrebljiva roba. Arhetipska slika hiperinflacije je trgovina sa praznim policama - potrošači brzo bježe iz propadajuće vrijednosti novca svoje nacije.

Nakon dovoljno vremena, kada je vjera potpuno uništena za vrijeme hiperinflacije, suvereni novac više nitko ne prihvaća, te se društvo može vratiti na robnu razmjenu, ili će doživjeti potpunu zamjenu monetarne jedinice za sredstvo razmjene. Primjer ovog procesa bila je zamjena zimbabveanskog dolara za američki dolar. Takva promjena suverenog novca za stranu valutu je dodatno otežana relativnom oskudnošću strane valute i odsustvom stranih bankarskih institucija koje pružaju likvidnost tržištu.
Sposobnost lakog prenošenja bitcoina preko granica i odsustvo potrebe za bankarskim sustavom čine Bitcoin idealnim monetarnim dobrom za one ljude koji pate pod hiperinflacijom. U nadolazećim godinama, kako fiat valute nastave svoj povijesni trend ka bezvrijednosti, Bitcoin će postati sve popularniji izbor za ušteđevine ljudi diljem svijeta. Kada je novac nacije napušten i zamijenjen Bitcoinom, Bitcoin će napraviti tranziciju iz spremišta vrijednosti u tom društvu u opće prihvaćeno sredstvo razmjene. Daniel Krawicz stvorio je termin “hiperbitcoinizacija” da bi opisao ovaj proces.
Učestala pogrešna shvaćanja
Većina ovog članka usredotočila se na monetarnu prirodu Bitcoina. Sa tim temeljima možemo adresirati neke od najčešćih nerazumijevanja u Bitcoinu.
Bitcoin je balon (bubble)
Bitcoin, kao sva tržišna monetarna dobra, posjeduje monetarnu premiju. Ona često rezultira uobičajenom kritikom da je Bitcoin samo “balon.” No, sva monetarna dobra imaju monetarnu premiju. Naprotiv, ta monetarna premija (cijena viša od one koju diktira potražnja za dobrom kao korisnim) je upravo karakteristična za sve oblike novca. Drugim riječima, novac je uvijek i svuda balon. Paradoksalno, monetarno dobro je istovremeno balon i ispod vrijednosti ukoliko je u ranijim stadijima općeg prihvaćanja kao novac.
Bitcoin je previše volatilan
Volatilnost cijene Bitcoina je funkcija njegovog nedavnog nastanka. U prvih nekoliko godina svojeg postojanja, Bitcoin se ponašao kao mala dionica, i svaki veliki kupac - kao npr. braća Winklevoss - mogao je uzrokovati veliki skok u njegovoj cijeni. No, kako su se prihvaćenost i likvidnost povećavali kroz godine, volatilnost Bitcoina je srazmjerno smanjila. Kada Bitcoin postigne tržišnu kapitalizaciju (vrijednost) zlata, imat će sličnu volatilnost kao i zlato. Kako Bitcoin nastavi rasti, njegova volatilnost će se smanjiti do razine koja ga čini prikladnim za široko korištenje kao medij razmjene. Kao što je prethodno rečeno, monetizacija Bitcoina se odvija u seriji Gartner hype ciklusa. Volatilnost je najniža za vrijeme vrhunaca i dolina unutar ciklusa. Svaki hype ciklus ima nižu volatilnost od prethodnih, zato što je likvidnost tržišta veća.
Cijene transakcija su previsoke
Novija kritika Bitcoin mreže je ta da ju je povećanje cijena prijenosa bitcoina učinilo neprikladnom za sustav plaćanja. No, rast u cijenama transakcija je zdrav i očekivan. One su nužne za plaćanje bitcoin minera (rudara), koji osiguravaju mrežu validacijom transakcija. Rudare se plaća kroz cijene transakcija ili kroz blok-nagrade, koje su inflacijska subvencija od trane trenutnih vlasnika bitcoina.
S obzirom na Bitcoinovu fiksnu proizvodnju (monetarna politika koja ga čini idealnim za spremanje vrijednosti), blok-nagrade će s vremenom nestati i mrežu će se u konačnici morati osiguravati kroz cijene transakcija. Mreža sa “niskim” cijenama transakcija je mreža sa slabom sigurnosti i osjetljiva na vanjsku intervenciju i cenzuru. Oni koji hvale niske cijene Bitcoinovih alternative zapravo niti ne znajući opisuju slabosti tih takozvanih “alt-coina.”
Površan temelj kritika Bitcoinovih “visokih” cijena transakcija je uvjerenje da bi Bitcoin trebao biti prvo sustav plaćanja, i drugo spremište vrijednosti. Kao što smo vidjeli kroz povijest novca, ovo uvjerenje je naopako. Samo onda kada Bitcoin postane duboko ukorijenjeno spremište novca može biti prikladan kao sredstvo razmjene. Nadalje, kada oportunitetni trošak razmjene bitcoina dođe na razinu koja ga čini prikladnim sredstvom razmjene, većina trgovine neće se odvijati na samoj Bitcoin mreži, nego na mrežama “drugog sloja” (second layer) koje će imati niže cijene transakcija. Takve mreže, poput Lightning mreže, služe kao moderna verzija zadužnica koje su korištene za prijenos vlasničkih papira zlata u 19. stoljeću. Banke su koristile zadužnice zato što je prijenos samog metala bio daleko skuplji. Za razliku od takvih zadužnica, Lightning mreža će omogućavati nisku cijenu prijenosa bitcoina bez potrebe za povjerenjem prema trećoj strani, poput banaka. Razvoj Lightning mreže je tehnološka inovacija od izuzetne važnosti u povijesti Bitcoina, i njezina vrijednost će postati očita u narednim godinama, kako je sve više ljudi bude razvijalo i koristilo.
Konkurencija
Pošto je Bitcoin softverski protokol otvorenog tipa (open-source), oduvijek je bilo moguće kopirati softver i imitirati mrežu. Kroz godine nastajali su mnogi imitatori, od identičnih kopija, kao Litecoin, do kompleksnijih varijanti kao što je Ethereum, koje obećavaju arbitrarno kompleksne ugovorne mehanizme koristeći decentralizirani računalni sustav. Česta kritika Bitcoinu od strane ulagača je ta da on ne može zadržati svoju vrijednost kada je vrlo lako stvoriti konkurente koji mogu lako i brzo u sebi imati najnovije inovacije i softverske funkcionalnosti.

Greška u ovom argumentu leži u manju takozvanog “mrežnog efekta” (network effect), koji postoji u prvoj i dominantnoj tehnologiji u nekom području. Mrežni efekt - velika vrijednost korištenja Bitcoina samo zato što je već dominantan - je važno svojstvo samo po sebi. Za svaku tehnologiju koja posjeduje mrežni efekt, to je daleko najvažnije svojstvo koje može imati.
Za Bitcoin, mrežni efekt uključuje likvidnost njegovog tržišta, broj ljudi koji ga posjeduju, i zajednicu programera koji održavaju i unaprjeđuju njegov softver i svjesnost u javnosti. Veliki ulagači, uključujući države, će uvijek prvo tražiti najlikvidnije tržište, kako bi mogli ući i izaći iz tržišta brzo, i bez utjecanja na cijenu. Programeri će se pridružiti dominantnoj programerskoj zajednici sa najboljim talentom, i time pojačati samu zajednicu. Svjesnost o brendu sama sebe pojačava, pošto se nadobudni konkurenti Bitcoina uvijek spominju u kontekstu Bitcoina kao takvog.
Raskrižje na putu (fork)
Trend koji je postao popularan 2017. godine nije bio samo imitacija Bitcoinovog softvera, nego kopiranje potpune povijesti njegovih prošlih transakcija (cijeli blockchain). Kopiranjem Bitcoinovog blockchaina do određene točke/bloka i odvajanjem sljedećih blokova ka novoj mreži, u procesu znanom kao “forking” (odvajanje), Bitcoinovi konkurenti su uspjeli riješiti problem distribuiranja svojeg tokena velikom broju korisnika.

Najznačajniji takav fork dogodio se 1. 8. 2017. godine, kada je nova mreža nazvana Bitcoin Cash (Bcash) stvorena. Vlasnik N količine bitcoina prije 1.8.2017. bi onda posjedovao N bitcoina i N BCash tokena. Mala, ali vrlo glasna zajednica Bcash proponenata je neumorno pokušavala prisvojiti Bitcoinov brend i ime, imenujući svoju novu mrežu Bitcoin Cast i pokušavajući uvjeriti nove pridošlice u Bitcoin da je Bcash “pravi” Bitcoin. Ti pokušaji su većinom propali, i taj neuspjeh se vidi u tržišnim kapitalizacijama dviju mreža. No, za nove ulagače, i dalje postoji rizik da bi konkurent mogao kopirati Bitcoin i njegov blockchain i tako uspjeti u preuzimanju tržišne kapitalizacije, te postati de facto Bitcoin.
Moguće je uočiti važno pravilo gledajući velike forkove u prošlosti Bitcoin i Ethereum mreža. Većina tržišne kapitalizacije odvijat će se na mreži koja zadrži najviši stupanj talenta i aktivnosti u zajednici programera. Premda se na Bitcoin može gledati kao na nov i mlad novac, on je također računalna mreža koja počiva na softveru, kojeg se pak treba održavati i poboljšavati. Kupovina tokena na mreži koja ima malo neiskusnih programera bilo bi kao kupovati kopiju Microsoft Windowsa na kojoj rade lošiji programeri. Jasno je vidljivo iz povijesti forkova koji su se odvili 2017. godine da su najbolji računalni i kriptografski stručnjaci posvećeni razvoju originalnog Bitcoina, a ne nekoj od rastućeg broja imitacija koje su se izrodile iz njega.
Stvarni rizici
Premda su uobičajene kritike upućene Bitconu od strane medija i ekonomske profesije krive i bazirane na netočnom shvaćanju novca, postoje pravi i značajni rizici kod ulaganja u Bitcoin. Bilo bi mudro za novog Bitcoin ulagača da shvati ove rizike prije potencijalnog ulaganja.
Rizik protokola
Bitcoin protokol i kriptografski sastavni dijelovi na kojima je sagrađen potencijalno imaju dosad nepronađenu grešku u svom dizajnu, ili mogu postati nesigurni razvojem kvantnih računala. Ako se pronađe greška u protokolu, ili neka nova metoda računarstva učini mogućim probijanje kriptografskih temelja Bitcoina, vjera u Bitcoin biti će znatno narušena. Rizik protokola bio je najviši u ranim godinama razvoja Bitcoina, kada je još uvijek bilo nejasno, čak i iskusnim kriptografima, je li Satoshi Nakamoto zaista riješio problem bizantskih generala (Byzantine Generals’ Problem). Brige oko ozbiljnih grešaka u Bitcoin protokolu nestale su kroz godine, no uzevši u obzir njegovu tehnološku prirodu, rizik protokola će uvijek ostati u Bitcoinu, makar i kao izuzetak.
Propadanje mjenjačnica
Time što je decentraliziran, Bitcoin je pokazao značajnu otpornost, suočen sa brojnim pokušajima raznih vlada da ga reguliraju ili unište. No, mjenjačnice koje trguju bitcoinima za fiat valute su centralizirani entiteti i podložne regulacijama i zatvaranju. Bez mjenjačnica i volje bankara da s njima posluju, proces monetizacije Bitcoina bio bi ozbiljno usporen, ako ne i potpuno zaustavljen. Iako postoje alternativni izvori likvidnosti za Bitcoin, poput “over-the-counter” brokera i decentraliziranih tržišta za kupovinu i prodaju bitcoina, kritičan proces otkrivanja i definiranja cijene se odvija na najlikvidnijim mjenjačnicama, koje su sve centralizirane.
Jedan od načina za umanjivanje rizika gašenja mjenjačnica je geografska arbitraža. Binance, jedna od velikih mjenjačnica iz Kine, preselila se u Japan nakon što joj je kineska vlada zabranila operiranje u Kini. Vlade su također oprezne kako ne bi ugušile novu industriju koja je potencijalno značajna kao i internet, i time predale nevjerojatnu konkurentnu vrijednost drugim nacijama.
Samo kroz koordinirano globalno ukidanje Bitcoin mjenjačnica bi proces monetizacije mogao biti zaustavljen. Trenutno smo u utrci; Bitcoin raste i postaje sve rašireniji, i doći će do trenutka kada bi potpuno ukidanje mjenjačnica postalo politički neizvedivo - kao i gašenje interneta. Mogućnost takvog ukidanja je još uvijek realna, i valja je uzeti u obzir pri ulaganju u Bitcoin. Kao što je gore objašnjeno, suverene vlade se polako bude i uviđaju prijetnju koju predstavlja neovisna digitalna valuta otporna na cenzuru, za njihovu monetarnu politiku. Otvoreno je pitanje hoće li išta poduzeti da odgovore ovoj prijetnji prije nego Bitcoin postane toliko utvrđen i raširen da politička akcija postane nemoćna i ne-efektivna.
Zamjenjivost
Otvorena i transparentna priroda Bitcoin blockchaina omogućava državama da proglase specifične bitcoine “okaljanima” zbog njihovog korištenja u određenim aktivnostima. Premda Bitcoin, na protokolarnoj razini, ne diskriminira transakcije na ikoji način, “okaljani” bitcoini bi mogli postati bezvrijedni ako bi ih regulacije proglasile ilegalnima i neprihvatljivima za mjenjačnice ili trgovce. Bitcoin bi tada izgubio jedno od kritičnih svojstava monetarnog dobra: zamjenjivost.
Da bi se ovaj problem riješio i umanjio, biti će potrebna poboljšanja na razini protokola kako bi se poboljšala privatnost transakcija. Premda postoji napredak u ovom smjeru, prvi put primjenjen u digitalnim valutama kao što su Monero i Zcash, potrebno je napraviti značajne tehnološke kompromise između efikasnosti i kompleksnosti Bitcoina i njegove privatnosti. Pitanje ostaje otvoreno je li moguće dodati nova svojstva privatnosti na Bitcoin, na način koji neće kompromitirati njegovu korisnost kao novca.
Zaključak
Bitcoin je novonastali novac koji je u procesu transformacije iz sakupljačkog dobra u spremište vrijednosti. Kao neovisno monetarno dobro, moguće je da će u budućnosti postati globalan novac, slično kao zlato za vrijeme 19. stoljeća. Prihvaćanje Bitcoina kao globalnog novca je upravo taj optimističan scenarij za Bitcoin, kojeg je artikulirao Satoshi Nakamoto još 2010. godine u email razmjeni sa Mikeom Hearnom:
"Ako zamisliš da se koristi u nekom dijelu svjetske trgovine, i da će postojati samo 21 milijun bitcoina za cijeli svijet, vrijednost po jedinici će biti znatno veća".
Ovaj scenarij je još snažnije definirao briljantni kriptograf Hal Finney, koji je ujedno primio i prve bitcoine od Nakamotoa, ubrzo nakon najave prvog funkcionalnog Bitcoin softvera:
"Zamislimo da Bitcoin bude uspješan i postane dominantan sustav plaćanja diljem svijeta. U tom slučaju će ukupna vrijednost valute biti jednaka ukupnoj vrijednosti svog bogatstva svijeta. Današnje procjene ukupnog svjetskog bogatska kućanstava koje sam pronašao borave negdje između 100 i 300 trilijuna dolara. Sa 20 milijuna bitcoina, svaki bi onda vrijedio oko 10 milijuna dolara."
Čak i da Bitcoin ne postane u cijelost globalan novac, nego da se samo natječe sa zlatom kao neovisno spremište vrijednosti, i dalje je masivno podcijenjen. Mapiranje tržišne kapitalizacije postojeće količine izrudarenog zlata (oko 8 trilijuna dolara) na maksimalnu dostupnost Bitcoina od 21 milijun, daje vrijednost od otprilike 380,000 dolara po bitcoinu. Kao što smo vidjeli u prethodnom tekstu, svojstva koja omogućavaju monetarnom dobru da bude prikladno spremište vrijednosti, čine Bitcoin superiornijim zlatu u svakom pogledu osim trajanja povijesti. No, kako vrijeme prolazi i Lindy efekt postane jači, dosadašnja povijest će prestati biti prednost zlata. Samim time, nije nerazumno očekivati da će Bitcoin narasti do, a možda i preko, ukupne cijene zlata na tržištvu do 2030. Opaska ovoj tezi je činjenica da veliki postotak vrijednosti zlata dolazi od toga što ga centralne banke čuvaju kao spremište vrijednosti. Da bi Bitcoin došao do te razine, određena količina suverenih država će trebati sudjelovati. Hoće li zapadnjačke demokracije sudjelovati u vlasništvu Bitcoina je nepoznato. Vjerojatnije je, nažalost, da će prve nacije u Bitcoin tržištu biti sitne diktature i kleptokracije.
Ako niti jedna država ne bude sudjelovala u Bitcoin tržištu, optimistična teza i dalje postoji. Kao nevisno spremište vrijednosti u rukama individualnih i institucionalnih ulagača, Bitcoin je i dalje vrlo rano u svojoj “krivulji prihvaćenosti” (adoption curve); tzv. “rana većina” ulaze na tržište sada, dok će ostali ući tek nekoliko godina kasnije. Sa širim sudjelovanjem individualnih i institucionalnih ulagača, cijena po bitcoinu između 100,000 i 200,000 dolara je sasvim moguća.
Posjedovanje bitcoina je jedna od malobrojnih asimetričnih novčanih strategija dostupnih svakome na svijetu. Poput “call” opcija, negativan rizik ulagača je ograničen na 1x, dok potencijalna dobit i dalje iznosi 100x ili više. Bitcoin je prvi istinski globalan balon čija je veličina ograničena samo potražnjom i željom građana svijeta da zaštite svoju ušteđevinu od raznovrsnih ekonomskih malverzacija vlade. Bitcoin je ustao kao feniks iz pepela globalne financijske krize 2008. godine - katastrofe kojoj su prethodile odluke centralnih banaka poput američke Federalne rezerve (Federal Reserve).
Onkraj samo financijske teze za Bitcoin, njegov rast i uspjeh kao neovisno spremište vrijednosti imat će duboke geopolitičke posljedice. Globalna, ne-inflacijska valuta će prisiliti suverene države da promjene svoje primarne mehanizme financiranja od inflacije u izravno oporezivanje; koje je daleko manje politički popularno. Države će se smanjivati proporcionalno političkoj boli koju im nanese oporezivanje kao jedini način financiranja. Nadalje, globalna trgovina vršiti će se na način koji zadovoljava aspiraciju Charlesa de Gaullea, da nijedna nacija ne bi smjela imati privilegiju nad ikojom drugom:
"Smatramo da je potrebno da se uspostavi međunarodna trgovina, kao što je bio slučaj prije velikih nesreća koje su zadesile svijet, na neosporivoj monetarnoj bazi, koja ne nosi na sebi oznaku ijedne države."
Za 50 godina, ta monetarna baza biti će Bitcoin.
-
 @ bf47c19e:c3d2573b
2025-05-11 21:32:19
@ bf47c19e:c3d2573b
2025-05-11 21:32:19Bitkoin, kao jedinstvena digitalna valuta, postaje poznat široj javnosti u trenutku kada se pojavljuju prvi znaci svetske ekonomske krize a postojeći finansijski sistem počinje da pokazuje sve svoje slabosti. Danas, bitkoin, izaziva veliku pažnju svojim naglim skokovima i padovima.
Osnovna ideja o o decentralizovanim valutama potekla je od osnivača kripto-pank pokreta, među kojima su bili direktori kompanija naprednih tehnologija, univerzitetski profesori i istraživači iz oblasti matematike i fizike. Njihova ideja zasnovana je na anonimnoj, istovremenoj komunikaciji koja neće biti kontrolisana i nadgledana od neke treće strane u procesu.
Šta je kriptovaluta, ko je njen tvorac, kako do nje doći, kako trgovati i gde je čuvati, neka su od pitanja za čijim odgovorima tragamo u emisiji.
Sagovornici u emisiji su svi oni koji su u poslednjih godinu dana bili relevantni učesnici priča o kriptovaluti u Srbiji: osnivači Asocijacije bitkoin, predstavnici Narodne banke Srbije i predstavnici medija.
Montažer Milan Radičević
Urednik Aleksandra Šarković
-
 @ 0fa80bd3:ea7325de
2025-01-30 04:28:30
@ 0fa80bd3:ea7325de
2025-01-30 04:28:30"Degeneration" or "Вырождение" ![[photo_2025-01-29 23.23.15.jpeg]]
A once-functional object, now eroded by time and human intervention, stripped of its original purpose. Layers of presence accumulate—marks, alterations, traces of intent—until the very essence is obscured. Restoration is paradoxical: to reclaim, one must erase. Yet erasure is an impossibility, for to remove these imprints is to deny the existence of those who shaped them.
The work stands as a meditation on entropy, memory, and the irreversible dialogue between creation and decay.
-
 @ 0fa80bd3:ea7325de
2025-01-29 15:43:42
@ 0fa80bd3:ea7325de
2025-01-29 15:43:42Lyn Alden - биткойн евангелист или евангелистка, я пока не понял
npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83aThomas Pacchia - PubKey owner - X - @tpacchia
npub1xy6exlg37pw84cpyj05c2pdgv86hr25cxn0g7aa8g8a6v97mhduqeuhgplcalvadev - Shopstr
npub16dhgpql60vmd4mnydjut87vla23a38j689jssaqlqqlzrtqtd0kqex0nkqCalle - Cashu founder
npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vgДжек Дорси
npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m21 ideas
npub1lm3f47nzyf0rjp6fsl4qlnkmzed4uj4h2gnf2vhe3l3mrj85vqks6z3c7lМного адресов. Хз кто надо сортировать
https://github.com/aitechguy/nostr-address-bookФиатДжеф - создатель Ностр - https://github.com/fiatjaf
npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6EVAN KALOUDIS Zues wallet
npub19kv88vjm7tw6v9qksn2y6h4hdt6e79nh3zjcud36k9n3lmlwsleqwte2qdПрограммер Коди https://github.com/CodyTseng/nostr-relay
npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wlAnna Chekhovich - Managing Bitcoin at The Anti-Corruption Foundation https://x.com/AnyaChekhovich
npub1y2st7rp54277hyd2usw6shy3kxprnmpvhkezmldp7vhl7hp920aq9cfyr7 -
 @ 8173f6e1:e488ac0f
2025-05-11 21:23:06
@ 8173f6e1:e488ac0f
2025-05-11 21:23:06TESTNOTEBIN2
-
 @ 0fa80bd3:ea7325de
2025-01-29 14:44:48
@ 0fa80bd3:ea7325de
2025-01-29 14:44:48![[yedinaya-rossiya-bear.png]]
1️⃣ Be where the bear roams. Stay in its territory, where it hunts for food. No point setting a trap in your backyard if the bear’s chilling in the forest.
2️⃣ Set a well-hidden trap. Bury it, disguise it, and place the bait right in the center. Bears are omnivores—just like secret police KGB agents. And what’s the tastiest bait for them? Money.
3️⃣ Wait for the bear to take the bait. When it reaches in, the trap will snap shut around its paw. It’ll be alive, but stuck. No escape.
Now, what you do with a trapped bear is another question... 😏
-
 @ 872982aa:8fb54cfe
2025-05-12 01:40:27
@ 872982aa:8fb54cfe
2025-05-12 01:40:27 {.user-img}
{.user-img}
-
 @ 8173f6e1:e488ac0f
2025-05-11 20:54:58
@ 8173f6e1:e488ac0f
2025-05-11 20:54:58testnotebin7testnotebin7testnotebin7testnotebin7
-
 @ 8173f6e1:e488ac0f
2025-05-11 20:50:24
@ 8173f6e1:e488ac0f
2025-05-11 20:50:24testnotebin123456testnotebin123456testnotebin123456testnotebin123456
-
 @ 872982aa:8fb54cfe
2025-05-12 01:39:07
@ 872982aa:8fb54cfe
2025-05-12 01:39:07 {.user-img}
{.user-img}

-
 @ bf47c19e:c3d2573b
2025-05-11 20:50:05
@ bf47c19e:c3d2573b
2025-05-11 20:50:05„Ova mašina ozelenjava“, koji predstavlja Swan Bitcoin, je dokumentarac koji istražuje složen i nijansiran odnos između Bitkoina i energije. Producent filma je Enrike Pozner, dok je režiser nagrađivani britanski filmski stvaralac Džejmi King čija je serija „Ukradi ovaj film“ (2006–2010) bila jedan od najpreuzimanijih dokumentaraca svih vremena.
U filmu „Ova mašina ozelenjava“ učestvuje glavna ekonomska savetnica Swan-a Lin Alden zajedno sa Aleksom Gladstajnom, Nikom Karterom i mnogim drugima. „Ova mašina ozelenjava“ razbija mnoge zablude o rudarenju Bitkoina i iznosi ubedljive argumente za Bitkoin kao neto-pozitivan faktor za životnu sredinu.
Prevod: bitcoin-balkan.com
-
 @ 9e69e420:d12360c2
2025-01-25 22:16:54
@ 9e69e420:d12360c2
2025-01-25 22:16:54President Trump plans to withdraw 20,000 U.S. troops from Europe and expects European allies to contribute financially to the remaining military presence. Reported by ANSA, Trump aims to deliver this message to European leaders since taking office. A European diplomat noted, “the costs cannot be borne solely by American taxpayers.”
The Pentagon hasn't commented yet. Trump has previously sought lower troop levels in Europe and had ordered cuts during his first term. The U.S. currently maintains around 65,000 troops in Europe, with total forces reaching 100,000 since the Ukraine invasion. Trump's new approach may shift military focus to the Pacific amid growing concerns about China.
-
 @ bf47c19e:c3d2573b
2025-05-11 20:24:44
@ bf47c19e:c3d2573b
2025-05-11 20:24:44Kratki dokumentarac zasnovan na istoimenoj knjizi Mareja Rotbarda. Teme uključuju: opasnosti koje sa sobom nosi država blagostanja, monetarne politike zasnovane na dugu, oporezivanje bez zastupanja i ostala sredstva državnog nasilja.
Autor filma: @rjames_BTC
Zvanični vebsajt filma: anatomystatefilm.com
Prevod: bitcoin-balkan.com
-
 @ 6be5cc06:5259daf0
2025-01-21 20:58:37
@ 6be5cc06:5259daf0
2025-01-21 20:58:37A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
-
 @ 33baa074:3bb3a297
2025-05-12 01:06:27
@ 33baa074:3bb3a297
2025-05-12 01:06:27Soil moisture is one of the key factors affecting crop root development. Too much or too little moisture will have an adverse effect on root growth.
Effect of excessive moisture When there is too much soil moisture, the following problems will occur:
Inhibit root respiration: Excessive moisture will squeeze out oxygen in the soil, causing root hypoxia, thereby inhibiting root respiration, and in severe cases, it can cause root growth to stop or rot and die. Affect soil aeration: Excessive moisture will reduce soil aeration and affect the normal growth of the root system. Effect of too little moisture When there is too little soil moisture, it will also have a negative impact on the root system:
Promote root corking and self-thinning: Lack of water can cause root corking and even self-thinning, affecting the absorption capacity of the root system.
Determine whether the soil moisture is appropriate In order to ensure the healthy development of crop roots, soil moisture needs to be managed reasonably. The following methods can be used to determine whether the soil moisture is appropriate:
Touch test: Use a small shovel to dig up the soil around the root system, grab some soil with your hand and pinch it in your hand. If the soil can be kneaded into a ball and can be spread apart, the moisture content is appropriate; if it can be kneaded into a ball but cannot be spread apart, the moisture content exceeds the standard; if it cannot be kneaded into a ball, the soil is lacking in water.
Conclusion In summary, soil moisture has an important impact on the development of crop roots. Reasonable water management is essential to promote healthy root growth. By monitoring and adjusting soil moisture through appropriate methods, the normal growth and development of crops can be effectively guaranteed.
-
 @ 9e69e420:d12360c2
2025-01-21 19:31:48
@ 9e69e420:d12360c2
2025-01-21 19:31:48Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits.
Active Compounds
The oil's therapeutic properties stem from its key bioactive components: - Carvacrol and thymol (primary active compounds) - Polyphenols and other antioxidant
Antimicrobial Properties
Bacterial Protection The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance.
Antifungal Effects It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections.
Digestive Health Benefits
Oregano oil supports digestive wellness by: - Promoting gastric juice secretion and enzyme production - Helping treat Small Intestinal Bacterial Overgrowth (SIBO) - Managing digestive discomfort, bloating, and IBS symptoms
Anti-inflammatory and Antioxidant Effects
The oil provides significant protective benefits through: - Powerful antioxidant activity that fights free radicals - Reduction of inflammatory markers in the body - Protection against oxidative stress-related conditions
Respiratory Support
It aids respiratory health by: - Loosening mucus and phlegm - Suppressing coughs and throat irritation - Supporting overall respiratory tract function
Additional Benefits
Skin Health - Improves conditions like psoriasis, acne, and eczema - Supports wound healing through antibacterial action - Provides anti-aging benefits through antioxidant properties
Cardiovascular Health Studies show oregano oil may help: - Reduce LDL (bad) cholesterol levels - Support overall heart health
Pain Management The oil demonstrates effectiveness in: - Reducing inflammation-related pain - Managing muscle discomfort - Providing topical pain relief
Safety Note
While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications.
-
 @ bf47c19e:c3d2573b
2025-05-11 20:15:51
@ bf47c19e:c3d2573b
2025-05-11 20:15:51U društvu koje koristi čvrst novac, jedini način sticanja bogatstva je stvaranje vrednosti za druge. Šta se jbt desilo 1971?
Autor filma: @rjames_BTC
Zvanični vebsajt: hardmoneyfilm.com
Prevod: bitcoin-balkan.com
-
 @ 33baa074:3bb3a297
2025-05-12 00:49:33
@ 33baa074:3bb3a297
2025-05-12 00:49:33Real-time monitoring of oil concentration in water The basic principle of oil in water sensor is to use the characteristic that oil will produce fluorescence under ultraviolet light, and measure the fluorescence intensity to infer the concentration of oil. The sensor uses ultraviolet light as the excitation light source to illuminate the water sample to be tested. The oil absorbs ultraviolet light and excites fluorescence. The fluorescence signal is received by the photo detector and converted into an electrical signal, and then the strength of the electrical signal is measured to determine the concentration of oil in the water sample, so as to achieve real-time monitoring of the concentration of oil in the water.
 Multi-scenario water quality monitoring
Water source water quality monitoring
It can be used to monitor the water quality of water sources. By continuously monitoring the oil in the water source, the pollution source can be found in time, thereby ensuring the safety of drinking water and water supply.
Multi-scenario water quality monitoring
Water source water quality monitoring
It can be used to monitor the water quality of water sources. By continuously monitoring the oil in the water source, the pollution source can be found in time, thereby ensuring the safety of drinking water and water supply.Sewage treatment plant discharge monitoring Sewage treatment plants may produce oily wastewater in the process of treating sewage. The oil-in-water sensor can monitor the water quality of its discharge to ensure that it meets the discharge standards and avoids secondary pollution to the environment.
Monitoring of water bodies such as rivers and lakes Water bodies such as rivers and lakes may be polluted by oil substances, such as ship leakage and industrial wastewater discharge. This sensor can monitor the water quality of these water bodies, evaluate the pollution status, and provide a basis for pollution control.
Aquaculture monitoring The online oil-in-water monitor (including oil-in-water sensor) can transmit monitoring data in real time to help farmers understand the water quality. Farmers can use it to understand the oil content in the water body in real time, and reasonably release it according to the needs of fish to improve the growth rate and health level of fish; it can also timely detect abnormal conditions in the water body, such as oil pollution and bacterial growth, and take corresponding measures to avoid the occurrence of diseases and reduce breeding costs and risks; at the same time, it helps farmers better understand the growth of fish, reasonably arrange fishing time, avoid overfishing and resource depletion, and promote the sustainable use of aquatic resources.
Early warning and emergency response It has real-time monitoring and early warning functions, and can issue an alarm in time when abnormal conditions of oil substances in the water body (such as exceeding the pee-set safety threshold) are found, providing valuable time for emergency response and reducing losses caused by pollution.
Assisting scientific research The monitoring data of the sensor can be used in scientific research fields such as ecology and environmental chemistry, helping researchers to gain a deeper understanding of the distribution, migration and transformation of oil substances in water bodies, and provide a scientific basis for environmental protection and governance.
Monitoring of pollution sources and environmental changes By detecting oil substances in water bodies, the location of pollution sources and the types of pollutants can be determined, providing a basis for finding and controlling pollution sources; it can also monitor oil pollutants in water bodies to understand the impact of environmental changes on water bodies and take timely measures to protect water sources.
-
 @ bf47c19e:c3d2573b
2025-05-11 19:29:26
@ bf47c19e:c3d2573b
2025-05-11 19:29:26"Misterija Satoši - Poreklo bitkoina" je francuski dokumentarno-animirani serijal koji dešifruje unutrašnje funkcionisanje bitkoin revolucije, dok istražuje identitet njenog tvorca.
Prvu decentralizovanu i pouzdanu kriptovalutu – bitkoin, osnovao je Satoši Nakamoto 3. januara 2009. godine. On je nestao 2011. i od tada ostaje anoniman, a njegov identitet je predmet svakakvih spekulacija. Tokom poslednjih 12 godina, vrednost bitkoina je porasla sa 0,001 na 69.000 dolara. Svi, od vlada do velikih korporacija, zainteresovali su se za Satošijev izum. Ko je Satoši Nakamoto? Kako je njegov izum postao toliko popularan? Šta nam bitkoin govori o svetu u kome živimo?
Ovaj serijal se prikazivao na Radio-televiziji Srbije (RTS 3) u sklopu novogodišnjeg muzičkog i filmskog programa 2022/2023. godine.
Naslov originala: "Le Mystère Satoshi"
Copyright: ARTE.TV
-
 @ bf47c19e:c3d2573b
2025-05-11 18:57:51
@ bf47c19e:c3d2573b
2025-05-11 18:57:51Originalni tekst na vice.com.
Davno pre nego što je postala šef najdesnije italijanske vlade od Drugog svetskog rata, Đorđa Meloni je kritikovala ono što je nazvala francuskom „kolonijalnom valutom“.
U snimku italijanske televizije iz 2019. koji je prošlog meseca postao megaviralan, Meloni je optužila Francusku da koristi CFA franak za eksploataciju resursa 14 afričkih zemalja i vrši finansijsku dominaciju nad njima. Određene stvari koje je tvrdila u videu nisu baš tačne, ali CFA franak jeste kontroverzan.
CFA franak je stvoren 1945. da bude valuta „francuskih kolonija u Africi“, a pošto Francuska kontroliše njegovo štampanje i promet, francuska vlada i dalje ima finansijsku kontrolu nad dobrim delom zapadnoafričke zemlje i više od 180 miliona ljudi. Dok su francuski zvaničnici ranije nazivali ovu valutu „činom velikodušnosti prema kolonijama“, o njenoj upotrebi se sada žestoko raspravlja.
Neke od afričkih nacija borile su se protiv valute, uključujući građane koji su razbijali prodavnice povezane sa Francuskom i osuđivali francuski jezik koji se uči u školama.
Jedna od onih 14 afričkih zemalja koja još uvek koristi CFA franak je Centralnoafrička Republika, država bez izlaza na more u kojoj živi oko 5 miliona ljudi i jedna od najsiromašnijih zemalja na svetu.
 Predsednik CAR Faustin-Aršanž Touadera govori na COP27 u Egiptu ranije ove godine. Foto: Gehad Hamdi/savez za slike preko Getti Image-a
Predsednik CAR Faustin-Aršanž Touadera govori na COP27 u Egiptu ranije ove godine. Foto: Gehad Hamdi/savez za slike preko Getti Image-aAli dok druge afričke nacije razmatraju odbacivanje CFA franka, CAR je jedna od prvih koja je zaista uradila nešto po tom pitanju, a ranije ove godine postala je prva zemlja u Africi i tek druga u svetu koja je usvojila Bitcoin kao legalnu valutu.
„Alternativa gotovini je kriptovaluta“, rekao je predsednik Faustin-Aršanž Touadera. „Za nas formalna ekonomija više nije opcija”.
Dok su prve najave o bitkoinu izazvale konfuziju, međunarodne nesuglasice i reakcije, vlada CAR-a je nastavila sa uvođenjem. Osam meseci kasnije, mnogi ljudi širom sveta, pa čak i građani CAR-a, možda nisu ni svesni da se promena dogodila.
U CAR samo 14 odsto stanovništva ima pristup električnoj energiji, a još manje – oko 10 odsto – može da koristi internet. A konflikt i dalje tinja i negativno utiče na zemlju i njenu ekonomiju već deceniju.
Na predstavljanju bitkoina, vlada CAR-a je rekla da će usvajanje valute promeniti bogatstvo zemlje i staviti CAR „na mapu najhrabrijih i najvizionarskijih zemalja sveta“.
Bitkoin ne kontroliše nikakva moć, tehnički je univerzalno dostupan i ne može se cenzurisati – što je velika promena u odnosu na drugu valutu nacije, ali prosečnom građaninu CAR bi bilo potrebno 60 godina da kupi jedan novčić.
 Žena maše francuskom zastavom uoči emitovanja polufinala Svetskog prvenstva između Francuske i Maroka u baru u Bangiju. Foto: BARBARA DEBOUT/AFP preko Getti Images
Žena maše francuskom zastavom uoči emitovanja polufinala Svetskog prvenstva između Francuske i Maroka u baru u Bangiju. Foto: BARBARA DEBOUT/AFP preko Getti ImagesU Bangiju – glavnom gradu CAR – studenti Univerziteta rekli su za VICE da se „ništa nije promenilo“ od velike najave vlade.
Studenti su želeli da ostanu anonimni jer su se plašili da negativno govore o ambicijama vlade. Pravo na slobodu izražavanja ne postoji u CAR, a građani često doživljavaju zastrašivanje i nasilje od strane provladinih milicija, oružanih grupa i snaga nacionalne bezbednosti.
„Bilo je ogromno slavlje kada je objavljen Bitcoin plan i svi smo bili ponosni na našu zemlju“, rekao je jedan 20-godišnjak, „ali ne mislim da se život ovde uopšte poboljšao od tada”.
Drugi student je dodao: „Nigde nema cena u radnjama izraženih u bitkoioni, niti iko traži od ljudi da plaćaju koristeći novu valutu. Većina trgovaca i kupaca na tržištu nemaju telefon ili internet. Posebno ljudi izvan Bangija, nemaju ništa““.
Aleks Lilaher, osnivač i izvršni direktor Rise Up Media – marketinške agencije koja radi sa bitkoin startapima – je saglasan sa studentima, rekavši za VICE koliko je „iznenađen” što je ta zemlja uopšte napravila takavpotez.
„Centralnoafrička Republika nije baš lider u tehnologiji na kontinentu, i činilo se da tamo nikada nije bilo mnogo bitkoin korisnika koji bi mogla da lobiraju za takav potez“, rekao je on.
 Pobednički tim slavi posle trke kanua za proslavu Dana nezavisnosti CAR-a u decembru. Fotografija: BARBARA DEBOUT/AFP preko Getti Images
Pobednički tim slavi posle trke kanua za proslavu Dana nezavisnosti CAR-a u decembru. Fotografija: BARBARA DEBOUT/AFP preko Getti ImagesUpitan da li građani CAR-a treba da vide usvajanje bitkoina kao pozitivnu ili negativnu stvar, Lilaher je odgovorio „ni jedno ni drugo, jer jednostavno ne mogu da vidim da će usvajanje uskoro krenuti. Ali imati alternativu i poslati signal Francuskoj da CAR želi da ima više nezavisnosti od valute je pozitivno u mojim očima”.
Dodaje: „Međutim, to takođe može imati posledice jer postoje moćne institucije poput Međunarodnog monetarnog fonda, na primer, sa kojima CAR mora da se bavi, koje nisu srećne što zemlje usvajaju bitkoin. Dakle, moglo bi doći do izazova sa kojima će vlada morati da se nosi“.
Centralnoafrička Republika je druga zemlja u svetu koja je usvojila bitkoin, a prva je El Salvador u septembru 2021. Lansiranje valute je tamo imalo različite rezultate, a nedavno je opisano kao „antiklimaktično“ i samo ga turisti zaista koriste.
Iako su ljudi možda očekivali da će druge nacije pratiti El Salvador, sigurno ne bi pomislili da će CAR odgovarati računu.
Glavna opoziciona stranka CAR-a bila je protiv tog predloga od samog početka. Banka centralnoafričkih država je takođe nazvala ovaj potez „problematičnim“ i navela da bi usvajanje valute uz CFA moglo ugroziti odnos nacije sa drugim afričkim zemljama.
Čak i kada većina ljudi u CAR-u nije mogla da investira u Bitcoin, i sve poruke upozorenja, u julu je vlada CAR-a lansirala sopstvenu kriptovalutu – „Sangocoin“. Sango je lokalni jezik koji se govori širom zemlje.
 Pripadnici teritorijalnog pešadijskog bataljona CAR marširaju tokom parade povodom Dana nezavisnosti u Bangiju. Fotografija: BARBARA DEBOUT/AFP preko Getti Images
Pripadnici teritorijalnog pešadijskog bataljona CAR marširaju tokom parade povodom Dana nezavisnosti u Bangiju. Fotografija: BARBARA DEBOUT/AFP preko Getti ImagesSangocoin neki vide kao budućnost CAR-a, a zahtevao je minimalnu investiciju od 500 dolara. Zauzvrat, investitori su mogli da kupe zemljište u zemlji bogatoj dijamantima za 10.000 dolara, pa čak i da kupe državljanstvo CAR-a za oko 60.000 dolara – iako je ove ponude kasnije blokirao najviši sud zemlje. Sangocoin investitori su takođe trenutno „zaključani“ za kupovinu, bez načina da kriptovalutu prodaju ili razmene.
Bio je to hrabar potez vlade, ali izgleda da se još uvek nije isplatio.
Ovog meseca, Centralnoafrička Republika je saopštila da odlaže puštanje nacionalne kriptovalute na kripto berze – što bi olakšalo međunarodnu trgovinu. Rojters kaže da je vlada okrivila „trenutne tržišne uslove” i „tržišne razloge”, ali je novinska agencija izračunala da je Sangocoin dostigao samo „0,01%” od najnovijeg vladinog cilja prodaje.
Još jedan skeptik je Aleks Gladštajn, glavni strateški službenik Fondacije za ljudska prava. On je dugogodišnji zagovornik usvajanja bitkoina u svetu u razvoju, kao i kritičar CFA franka – ali čak i on oseća da je CAR-ova šema bila „izuzetno neosmišljena“.
„Iako imam mnogo simpatije prema ranjivoj i siromašnoj naciji koja usvaja bitkoin kao drugu valutu – posebno naciji koja je decenijama i decenijama finansijski kontrolisana od strane svoje bivše kolonijalne sile, nisam baš optimističan u pogledu toga kako je to izvedeno“, rekao je za VICE.
 Manekenka učestvuje na prvoj nedelji mode u centralnoj Africi u Bangiju u decembru. Fotografija: BARBARA DEBOUT/AFP preko Getti Images
Manekenka učestvuje na prvoj nedelji mode u centralnoj Africi u Bangiju u decembru. Fotografija: BARBARA DEBOUT/AFP preko Getti ImagesDodao je: „Zaista se čini da je cela ova stvar bila kao prevara da se Sangocoin promoviše. Ne mislim da je cilj bio da se bitkoin integriše na smislen način u ekonomiju zemlje. Čini se da je predsednik zainteresovan za bitkoin i da postoji mala grupa ljudi oko njega koja je iskoristila taj interes da bi mogla da donese ove zakone kako bi pokušala da pokrene Sangocoin, od kojeg su imali viziju da zarade gomilu novca. Ali izgleda da je na kraju uspela da prikupi samo malo novca.”
Gladstein kaže da bi Bitcoin mogao biti „veoma važna finansijska tehnologija za ljude Centralnoafričke Republike tokom vremena, i pametno je da vlada istraži kako to može pomoći ljudima“, ali je potrebno mnogo posla da se to postigne.
Vlada Centralnoafričke Republike i opoziciona vlada nisu odgovorile na nekoliko zahteva za intervju.
Tekst podržao Omidiar Netvork. VICE World News zadržava potpunu uređivačku autonomiju.
-
 @ 6be5cc06:5259daf0
2025-01-21 01:51:46
@ 6be5cc06:5259daf0
2025-01-21 01:51:46Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas.
Satoshi Nakamoto
satoshin@gmx.com
www.bitcoin.org
Resumo
O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado gasto duplo, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações.
As transações são registradas em um livro público chamado blockchain, protegido por uma técnica chamada Prova de Trabalho. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira.
Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu.
1. Introdução
Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em confiança.
Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável.
Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável.
O que precisamos é de um sistema de pagamento eletrônico baseado em provas matemáticas, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas.
Neste documento, apresentamos o Bitcoin, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques.
2. Transações
Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital.
O que é uma assinatura digital?
Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso.
Como funciona na prática?
Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário:
- A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1.
- Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2.
- Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda.
Resolvendo o problema do gasto duplo
Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro.
O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain.
Por que isso é importante?
Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes.
3. Servidor Timestamp
Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica.
Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público.
Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain.
Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada.
O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin.
4. Prova-de-Trabalho
Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente.
A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita.
Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain.
A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos.
Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional.
5. Rede
A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são:
-
Transmissão de Transações: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la.
-
Coleta de Transações em Blocos: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain).
-
Prova-de-Trabalho: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil.
-
Envio do Bloco Resolvido: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede.
-
Validação do Bloco: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos.
-
Construção do Próximo Bloco: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia.
Resolução de Conflitos e Escolha da Cadeia Mais Longa
Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia.
Tolerância a Falhas
A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido.
Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central.
6. Incentivo
O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação.
Recompensa por Mineração
Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho.
Taxas de Transação
Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo.
Incentivo à Honestidade
O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas:
- Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos.
- Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas.
A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema.
Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo.
7. Recuperação do Espaço em Disco
Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações.
Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados.
Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados.
Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo.
8. Verificação de Pagamento Simplificada
É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada.
Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação.
A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede.
Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável.
9. Combinando e Dividindo Valor
No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor.
Entradas e Saídas
Cada transação no Bitcoin é composta por:
- Entradas: Representam os valores recebidos em transações anteriores.
- Saídas: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente.
Normalmente, uma transação contém:
- Uma única entrada com valor suficiente para cobrir o pagamento.
- Ou várias entradas combinadas para atingir o valor necessário.
O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como troco.
Exemplo Prático
Imagine que você tem duas entradas:
- 0,03 BTC
- 0,07 BTC
Se deseja enviar 0,08 BTC para alguém, a transação terá:
- Entrada: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC).
- Saídas: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC).
Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente.
Difusão e Simplificação
A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade.
10. Privacidade
O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando chaves públicas anônimas, que desvinculam diretamente as transações das identidades das partes envolvidas.
Fluxo de Informação
- No modelo tradicional, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário.
- No Bitcoin, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não.
Protegendo a Privacidade
Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas:
- Chaves Públicas Anônimas: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único.
- Prevenção de Ligação: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário.
Riscos de Ligação
Embora a privacidade seja fortalecida, alguns riscos permanecem:
- Transações multi-entrada podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total.
- O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas.
11. Cálculos
Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito.
Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira.
Mas isso é extremamente difícil.
Como o Ataque Funciona
Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido.
- Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira.
- O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida.
Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente.
A Corrida Entre Cadeias
Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos.
Suponha que:
- A rede honesta tem 80% do poder computacional (ou seja, resolve 8 de cada 10 quebra-cabeças).
- O atacante tem 20% do poder computacional (ou seja, resolve 2 de cada 10 quebra-cabeças).
Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar.
Por Que o Ataque Fica Cada Vez Mais Improvável?
Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos:
P = (q/p)^z
- q é o poder computacional do atacante (20%, ou 0,2).
- p é o poder computacional da rede honesta (80%, ou 0,8).
- z é a diferença de blocos entre a cadeia honesta e a cadeia do atacante.
Se o atacante está 5 blocos atrás (z = 5):
P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%)
Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável.
Se ele estiver 10 blocos atrás (z = 10):
P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%).
Neste caso, as chances de sucesso são praticamente nulas.
Um Exemplo Simples
Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível.
No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática.
Por Que Tudo Isso é Seguro?
- A probabilidade de sucesso do atacante diminui exponencialmente. Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema.
- A cadeia verdadeira (honesta) está protegida pela força da rede. Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar.
E Se o Atacante Tentar Continuar?
O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil.
Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso.
12. Conclusão
Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos.
Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
-
 @ 99e7936f:d5d2197c
2025-05-11 18:40:50
@ 99e7936f:d5d2197c
2025-05-11 18:40:50Wir sprechen kein Wort mehr miteinander, weil es weh tut
Viele Menschen haben in den letzten Jahren den Kontakt zu wichtigen Bezugspersonen verloren. Viele Menschen haben auch neue Leute auf der Straße oder durch Netzwerke kennen gelernt. Und manche Menschen hatten das Glück, schon vor der inszenierten Krise einen unterstützenden und stabilen Freundeskreis zu haben und haben diesen immer noch. Manchmal kommen alte Leute wieder zurück ins Leben, weil sie merken, dass man es gut mit ihnen meinte, als man vor den unglaublichen Lügen der Amtsträger warnte. Manchmal kommen alte Leute auch nicht mehr zurück, weil die Scham, auf falsche Versprechen herein gefallen zu sein, zu groß ist. Man gibt sich dann nach außen unverändert souverän und zieht es vor, still und heimlich zu leiden. Die neuen Kontakte bestehen manchmal leider auch nur temporär, sind zweckgebunden. Kaum ist die gemeinsame Aufgabe vollbracht, trennen sich die Wege wieder.
All das muss man in diesen Tagen gehäuft aushalten. Alles verändert sich in stärkerem Maße als sonst. Viele dieser Veränderungen tun weh. Man kann sich auf Trauma nicht vorbereiten. Nie.
Ich möchte jetzt keine schlichten Alltagsbeobachtungen darüber widergeben, wie ich selbst oder Menschen in meinem Umfeld in den letzten Jahren ihre Beziehungen erlebt haben. Vielmehr geht es mir auch in diesem Artikel wieder um das Thema Trauma und um die Folgen, die jedes einzelne Trauma auch gesamtgesellschaftlich betrachtet hat. Was passiert, wenn man eine bereits durch Kriege traumatisierte Gesellschaft noch zusätzlich jahrelang unter Druck setzt, so wie dies in den letzten fünf Jahren geschehen ist? Wieviel Trauma verträgt eine Gesellschaft? Wie verändern sich Beziehungen in einer Gesellschaft, die immer wieder erneut traumatisiert wird? Ist irgendwann das Maß des Erträglichen voll? Und wenn ja, wie äußert sich solch eine Kumulation von Traumafolgen?
Meines Erachtens sehen wir gerade genau die Ergebnisse solch einer Kumulation von Traumafolgen in unserer deutschen Gesellschaft, vielleicht sogar global: Menschen reden nicht mehr (vertieft) miteinander. Und dies ist nur eine von vielen Traumafolgen.
Ich freue mich über jeden Leser, der jetzt noch weiterliest.
Durch genügend Traumatisierung kann man Menschen offensichtlich zeitweise dazu bringen, dass sie nicht mehr (vertieft) miteinander reden, weil das Reden weh tut.
Traumatisierung ist daher eine effektive Strategie der vermeintlich Herrschenden, Menschen zu separieren.
Traumatisierung setzt tiefe Verletzungen und macht Menschen vorübergehend sprachlos. Es fehlen einem die Worte. Man möchte dann nicht reden. Aber man verschließt sich auch vor den Worten anderer, weil man keine weitere Verletzung mehr erträgt.
Menschen im Alltag erachten es vielleicht mittlerweile schon als normal, wenn Beziehungen nicht gut laufen, egal, um welche Art von Beziehung es sich handelt. Sobald Probleme auftauchen, wird erst kurz gestritten, dann geschwiegen und wenn man das Schweigen nicht mehr aushält, dann gibt es entweder noch einen Versuch oder man geht gleich auf Distanz und bricht den Kontakt ganz ab. Auch meine Zündschnur ist manchmal immer noch gefühlt zu kurz. Wenn man sich Distanz nicht erlauben kann, dann frisst man das Problem in sich hinein, spült es runter, kompensiert irgendwie, wartet darauf, dass sich von allein etwas ändert oder dass sich eine bessere Gelegenheit bietet, bei der man dann die Biege machen kann. Mehrere Eisen im Feuer zu haben, beruflich wie privat, gilt als clever. Probleme nicht anzusprechen, gilt als kompetent. Das Wort Teamfähigkeit ist im Berufsleben zu einem Kampfbegriff geworden. Wer im Arbeitskontext Probleme anspricht, ist offensichtlich nicht teamfähig. Die Frage „Sind Sie teamfähig?“, erzählt meines Erachtens mehr über den Chef als über den Mitarbeiter. Die passendere Frage wäre wohl „Können Sie sich wortlos an schlechte Zustände dauerhaft adaptieren?“ In privaten Beziehungen braucht man, wenn es nicht so gut läuft, einen stilvollen Urlaub oder eine neue Wohnzimmereinrichtung, um endlich mal wieder schöne Gefühle erleben zu können. Negative Gefühle sind scheinbar das Kind, das keiner haben wollte, weshalb es die schönsten Kleider bekommt. Auch ich kenne Ablenkung von negativen Gefühlen durch Konsum und Essen. Es lohnt sich, mal den Werbeslogans von Möbelhäusern, Ferienanbietern oder Lebensmittelhändlern bewusst zuzuhören. Die Werbung kennt unsere Sehnsüchte und damit auch unsere negativen Gefühle besser als wir selbst. Und für alle, die nicht konsumieren wollen, die nicht locker lassen und steif darauf beharren, dass es aber ein Problem in der Beziehung oder am Arbeitsplatz oder zumindest eine gewisse Unzufriedenheit gäbe, für diese Menschen gibt es garantiert ein passendes Coaching- oder Weiterbildungsprogramm mit Namen wie „In 12 Modulen zur Selbstentfaltung“, welches nur deshalb meist nicht funktioniert, weil man es angeblich nicht richtig durchgeführt hat oder vorab noch das Basismodul absolvieren muss. Bildung ist mittlerweile auch ein Markt, der Konsumgüter in Form von Coachings und Seminaren anbietet.
Auch ich bin übrigens lange zusammen gezuckt bei der Frage „Sind sie teamfähig?“ oder der Feststellung „Du bist das Problem, weil Du immer alles so genau nimmst, nicht die Fünf gerade sein lassen kannst.“ Am Ende ist man immer der Dumme, wenn man ein negatives Gefühl hat und darüber sprechen möchte. Trauma löst Scham UND Wut in einer Person aus. Scham zieht Abwertung an wie Licht die Motten anzieht. Und irgendwann platzt einem der Kragen. Man teilt selber aus. Und dann schämt man sich erneut, nicht nur für das früher oder später erlittene Trauma im Leben, sofern einem das bewusst ist, sondern auch für die unbeherrschte Reaktion, die man oft selbst nicht richtig versteht. Nicht bearbeitetes Trauma arbeitet unbewusst in uns.
Eine traumatisierte Gesellschaft wertet sich ständig gegenseitig ab und hält genau damit die Wunden offen.
Dann ist es vielleicht doch besser, das Problem in der Beziehung oder am Arbeitsplatz runter zu schlucken, auf Distanz zum anderen zu gehen, sich schon mal nach einer neuen Wohnzimmereinrichtung, einem neuen Partner oder einem neuen Job umzuschauen? Ich denke nicht, dass das eine Lösung ist.
Hinschauen und Gefühle bei sich und anderen zulassen, ist ein guter Anfang.
Wir gehen oft Beziehungen ein, gehen aber gleichzeitig einer echten tiefen und anhaltenden Verbindungen privat wie beruflich instinktiv aus dem Weg, weil echte tiefe Gespräche, zu denen es in solchen Verbindungen kommen kann, weh tun können, insbesondere wenn man noch unverarbeitetes Trauma mit sich herum schleppt. Und in einer traumatisierten Gesellschaft, tragen halt viele Menschen solche traumatisierten und nicht bearbeiteten Anteile mit sich herum.
Wir sind die Kinder und Kindeskinder der Menschen, die den zweiten Weltkrieg hautnah miterlebt haben. Alles, was die Eltern und Großeltern nicht besprochen, nicht verarbeitet haben, tragen wir weiter mit uns herum. Das ist den meisten Menschen, meines Erachtens, nicht bewusst. Mag sein, dass an dieser Stelle der eine oder andere widerspricht. Widersprechen Sie mir gerne. Meine Alltagserfahrung ist eine andere. Die Art, wie wir Beziehungen gestalten, spricht Bände. Aber, wenn man es nicht anders kennt und keine Kontrollgruppe hat, sagt man sich halt: „So isses. Und so isses normal. Ich kenne es nicht anders. Das machen doch alle so.“
Es ist so normal, in unserer Gesellschaft, nicht vertieft über negative (und auch positive) Gefühle zu reden. Alleine die Bezeichnung „negative Gefühle“ klingt schon wenig einladend. Und es ist auch so normal, Menschen in dem Moment, wo sie gegen jede Empfehlung nicht nur über negative Gefühle reden wollen, sondern diese sogar live und in Farbe zeigen, abzuwerten, oder noch schlimmer, zu ignorieren, weil man sich verunsichert fühlt, nicht weiß, wie man damit umgehen soll. Gefühle scheinen ansteckend zu sein. Da ist Vorsicht geboten. Ich persönlich kann mich an viele solcher Momente erinnern, wo Menschen nicht gern hören wollten, wovor ich Angst hatte, was und wer mich verletzt und wütend gemacht hatte, beruflich wie privat. Mit geäußerter Angst und Trauer macht man(n) sich ganz schnell lächerlich. Mit Wut hingegen wird ein Mann von anderen als stark bis beängstigend wahrgenommen. Ein Mann, der wütend agiert, wird eher als kraftvoll und temperamentvoll eingeschätzt. Eine Frau wird mit Wut dann akzeptiert, wenn sie bereits in einer (männlichen) Führungsrolle ist. „Sie“ muss schließlich ihren „Mann“ stehen. Hat sie keine Führungsrolle, wird sie abgewertet oder befördert. Dem wütenden Mann wird eher unterstellt, er habe schließlich einen wichtigen Auftrag zu erfüllen. Der Frau wird eher ein Mangel unterstellt, den ich hier nicht näher bezeichnen möchte. Darin spiegeln sich sehr starre Rollenvorstellungen von Mann und Frau in unserer Gesellschaft wider. Ängstliche Frauen, die bei einer Autopanne bezaubernd aussehen, erfüllen ein bestimmtes Klischee. Impulsive Männer mit Holzfällerhemd erfüllen zumindest auf einer Baustelle ein anderes Klischee. Menschen mit ausgeprägten negativen Gefühlen werden unter bestimmten Umständen glorifiziert. Der bezaubernd aussehenden Frau mit Autopanne wird schnell und gerne geholfen. Aber wenn die ängstliche Frau eine Vorgesetzte ist und der impulsive Mann mit Holzfällerhemd ein Kunde in einem Beratungsbüro ist, dann kann die Bewertung ganz anders ausfallen. Dann sind diese Gefühle vermeintlich fehlplatziert. Gefühle scheinen einen Platz zu haben. Die ängstliche Vorgesetzte hat eine Führungsschwäche und der impulsive Kunde im Beratungsbüro wird vom Sicherheitsdienst „entfernt“. Der Wunsch, über die gezeigten negativen Gefühle zu reden, wird einem mit Nachdruck verwehrt. Durch diesen vermeidenden Umgang mit negativen Gefühlen oder die Fehlinterpretation dieser Gefühle kommt es meines Erachtens oft zu bestimmten Rollenbesetzungen im Berufsleben. Eine positive Selektion von Mitarbeitern mit sehr rücksichtslosem oder überangepasstem Verhalten findet statt. In privaten Beziehungen werden negative Gefühle durch Ablenkung und Konsum vermieden. Es werden zu viele oder zu wenige Kontakte gepflegt. Beziehungen werden gar nicht mehr für die Ewigkeit antizipiert. Man hält sich alle Wege offen und lernt ständig neue Leute kennen. Oder man lebt Beziehung in sehr starren Strukturen, wo neue Informationen kaum Eingang finden, damit man sich nicht hinterfragen und mit anderen vergleichen muss. Lebensphasen mit dem weit geöffneten oder dem eher geschlossenen Muster wechseln sich auch manchmal ab. Individuelle Entwicklungen des einen oder anderen Musters in Lebensverläufen, zeichnen sich irgendwann als gesellschaftliche Strömung ab, wenn sie bei vielen Menschen gleichzeitig geschehen. Menschen wollen alles ausprobiert haben, bevor sie sich das Reihenhaus kaufen. Andere verkaufen ihr Reihenhaus nach der Scheidung, um im Wohnmobil durch die Welt zu tingeln. Man könnte denken, dass dies einfach individuelle Lebensverläufe sind, die sich zufällig so ergeben haben. Es gab Zeiten, wo Menschen zufällig viel Halt in starren Beziehungs- und Lebensstrukturen fanden. Gegenbewegungen brachen diese starren Strukturen nicht wirklich auf, weil sie Feuer mit Feuer bekämpften. Grundsätzlich gegen alles zu sein, was die Eltern vorgelebt haben, ist ja auch irgendwie rigide. Der Apfel fällt nicht zufällig neben den Stamm. Heute 80 Jahre nach Kriegsende können Menschen mit Begriffen wie Achtsamkeit und bewusster Kommunikation immer mehr anfangen, jedoch geht die weit verbreitete Bewusstheit und Selbstreflektiertheit oft zu Lasten einer wünschenswerten Verarbeitungstiefe. Zu oft werden wir gedacht, gefühlt und gelenkt. Um dies mit uns machen zu können, werden von vermeintlich Herrschenden wichtige Orientierungspunkte wie die eigene Geschichte, Kultur und Sprache falsch erzählt oder bis zur Unkenntlichkeit verändert. Und eigene Gefühle, die einem noch letzten Halt und Orientierung in diesem Dschungel bieten könnten, werden vom Kapitalismus ausdauernd gejagt wie ein seltenes Tier. Separierung und Orientierungslosigkeit ist gewollt.
Alles dreht sich um unsere tiefen Gefühle, insbesondere diese negativen Gefühle, die aus Trauma entstehen. Diese Gefühle wollen gesehen, gehört und bearbeitet werden. Sie machen zum Glück, solange es die Menschheit gibt, zuverlässig auf sich selbst aufmerksam. Sie sind in Wahrheit unsere Lebensversicherung. Die Zeit heilt gar nichts. Und hierfür braucht es wieder ein Bewusstsein, dass Gefühle wertvoll sind, auch solche, die aus Trauma entstehen. Ich persönlich habe dafür mehr als ein halbes Leben gebraucht, um dies zu verstehen. Als junge Frau habe ich nicht gewusst, dass viele meiner Gefühle, negativ wie positiv, Ausdruck meines Traumas waren. Heute weiß ich, dass ich mit dieser Einschätzung, die ich damals hatte, in „guter Gesellschaft“ war. Den meisten Menschen geht das so, bis sie irgendwann ihr eigenes Trauma erkennen.
Wir sind eine traumatisierte Gesellschaft, und die Arten und Ausprägungen von Trauma sind so vielfältig und den meisten Menschen unbekannt wie die Namen der Blumen auf einer Sommerwiese.
Wenn man diesen Satz wirken lässt, dann stellt sich doch die Frage:
Wie sieht denn ein gesunder Umgang mit negativen (und positiven) Gefühlen aus?
Reicht es aus, wenn man die Namen aller Wiesenblumen auswendig lernt, damit man jedes Trauma genau bestimmen kann? Oder geht es mehr um das Fühlen und weniger um das Wissen?
Den gesunden Umgang mit meinen Gefühlen habe ich nicht durch Theorie und Bücher erlernt, sondern durch den Alltag, durch die (emotionalen) Reaktionen meiner Mitmenschen und durch das bewusste Spüren und Zulassen meiner eigenen Gefühle. In Stufen lernte ich meine Gefühle immer besser kennen und mit ihnen umzugehen. Je besser ich sie kannte, umso lieber waren sie mir. Und ich lerne sie immer noch weiter und besser kennen. Das ist ein Prozess.
Traumabearbeitung ist anfangs ein anstrengender Prozess. Man sollte das langsam angehen. Aber diese Arbeit ist sehr lohnenswert, weil sie einem viele glückliche Momente, Kraft und Lebensfreude schenkt. Reden wird dadurch leichter und bringt in allen Lebensbereichen Fortschritte. Manchmal tut Reden auch weh (siehe Titel), aber zeitgleich, und auch langfristig gesehen, wird das Leben schöner durch Traumabearbeitung. Es geht nicht um Schmerzvermeidung, sondern darum, mit dem Schmerz gut umgehen zu können. Denn dadurch wird er letztlich kleiner und verwandelt sich zur Wiesenblume. Es geht um Verwandlung durch Fühlen. Die Erfahrung, dass man Trauma bearbeiten kann, erzählt mir so viel über dieses Leben, wie stark es ist, wie sehr es uns liebt und welche Blüten daraus wachsen können. Viele schöne Dinge, die wir täglich sehen, sind aus bewältigtem Trauma oder dem Wunsch, Trauma zu bewältigen, entstanden.
Der Schmerz lehrt uns Demut vor dem Leben und kreiert nebenbei die schönsten Lieder und Kunstwerke. Trauer und Verlust betonen den Wert der Dinge. Ärger und Wut bringen uns in Wallungen und stellen die Energie bereit, die man manchmal braucht, um Berge zu versetzen. Ängste sind das Tor zum Glück. Schuld und Scham lehren uns Vergebung. Neid und Eifersucht lassen unseren Selbstwert wachsen, wenn wir uns ihnen stellen. Und Freude, Glück und Ekstase machen uns dankbar, großzügig und optimistisch.
Wenn wir diese Gefühle wieder zulassen, dann können wir gar nicht anders als reden. Wir reden dann wieder vertieft miteinander, weil es gut tut, weil es entlastet, weil es Nähe zu anderen vielleicht erstmalig aufbaut und dann zu einem dicken Band verstärkt bis ein großes stabiles Netz daraus entsteht, welches Menschen, die gerade Halt benötigen, diesen bieten kann.
Wir reden dann wieder miteinander, weil es gut tut.
-
 @ cff1720e:15c7e2b2
2025-01-19 17:48:02
@ cff1720e:15c7e2b2
2025-01-19 17:48:02Einleitung\ \ Schwierige Dinge einfach zu erklären ist der Anspruch von ELI5 (explain me like I'm 5). Das ist in unserer hoch technisierten Welt dringend erforderlich, denn nur mit dem Verständnis der Technologien können wir sie richtig einsetzen und weiter entwickeln.\ Ich starte meine Serie mit Nostr, einem relativ neuen Internet-Protokoll. Was zum Teufel ist ein Internet-Protokoll? Formal beschrieben sind es internationale Standards, die dafür sorgen, dass das Internet seit über 30 Jahren ziemlich gut funktioniert. Es ist die Sprache, in der sich die Rechner miteinander unterhalten und die auch Sie täglich nutzen, vermutlich ohne es bewusst wahrzunehmen. http(s) transportiert ihre Anfrage an einen Server (z.B. Amazon), und html sorgt dafür, dass aus den gelieferten Daten eine schöne Seite auf ihrem Bildschirm entsteht. Eine Mail wird mit smtp an den Mailserver gesendet und mit imap von ihm abgerufen, und da alle den Standard verwenden, funktioniert das mit jeder App auf jedem Betriebssystem und mit jedem Mail-Provider. Und mit einer Mail-Adresse wie roland@pareto.space können sie sogar jederzeit umziehen, egal wohin. Cool, das ist state of the art! Aber warum funktioniert das z.B. bei Chat nicht, gibt es da kein Protokoll? Doch, es heißt IRC (Internet Relay Chat → merken sie sich den Namen), aber es wird so gut wie nicht verwendet. Die Gründe dafür sind nicht technischer Natur, vielmehr wurden mit Apps wie Facebook, Twitter, WhatsApp, Telegram, Instagram, TikTok u.a. bewusst Inkompatibilitäten und Nutzerabhängigkeiten geschaffen um Profite zu maximieren.

Warum Nostr?
Da das Standard-Protokoll nicht genutzt wird, hat jede App ihr eigenes, und wir brauchen eine handvoll Apps um uns mit allen Bekannten auszutauschen. Eine Mobilfunknummer ist Voraussetzung für jedes Konto, damit können die App-Hersteller die Nutzer umfassend tracken und mit dem Verkauf der Informationen bis zu 30 USD je Konto und Monat verdienen. Der Nutzer ist nicht mehr Kunde, er ist das Produkt! Der Werbe-SPAM ist noch das kleinste Problem bei diesem Geschäftsmodell. Server mit Millionen von Nutzerdaten sind ein “honey pot”, dementsprechend oft werden sie gehackt und die Zugangsdaten verkauft. 2024 wurde auch der Twitter-Account vom damaligen Präsidenten Joe Biden gehackt, niemand wusste mehr wer die Nachrichten verfasst hat (vorher auch nicht), d.h. die Authentizität der Inhalte ist bei keinem dieser Anbieter gewährleistet. Im selben Jahr wurde der Telegram-Gründer in Frankreich in Beugehaft genommen, weil er sich geweigert hatte Hintertüren in seine Software einzubauen. Nun kann zum Schutz "unserer Demokratie” praktisch jeder mitlesen, was sie mit wem an Informationen austauschen, z.B. darüber welches Shampoo bestimmte Politiker verwenden.

Und wer tatsächlich glaubt er könne Meinungsfreiheit auf sozialen Medien praktizieren, findet sich schnell in der Situation von Donald Trump wieder (seinerzeit amtierender Präsident), dem sein Twitter-Konto 2021 abgeschaltet wurde (Cancel-Culture). Die Nutzerdaten, also ihr Profil, ihre Kontakte, Dokumente, Bilder, Videos und Audiofiles - gehören ihnen ohnehin nicht mehr sondern sind Eigentum des Plattform-Betreibers; lesen sie sich mal die AGB's durch. Aber nein, keine gute Idee, das sind hunderte Seiten und sie werden permanent geändert. Alle nutzen also Apps, deren Technik sie nicht verstehen, deren Regeln sie nicht kennen, wo sie keine Rechte haben und die ihnen die Resultate ihres Handelns stehlen. Was würde wohl der Fünfjährige sagen, wenn ihm seine ältere Schwester anbieten würde, alle seine Spielzeuge zu “verwalten” und dann auszuhändigen wenn er brav ist? “Du spinnst wohl”, und damit beweist der Knirps mehr Vernunft als die Mehrzahl der Erwachsenen. \ \ Resümee: keine Standards, keine Daten, keine Rechte = keine Zukunft!

\ Wie funktioniert Nostr?
Die Entwickler von Nostr haben erkannt dass sich das Server-Client-Konzept in ein Master-Slave-Konzept verwandelt hatte. Der Master ist ein Synonym für Zentralisierung und wird zum “single point of failure”, der zwangsläufig Systeme dysfunktional macht. In einem verteilten Peer2Peer-System gibt es keine Master mehr sondern nur gleichberechtigte Knoten (Relays), auf denen die Informationen gespeichert werden. Indem man Informationen auf mehreren Relays redundant speichert, ist das System in jeglicher Hinsicht resilienter. Nicht nur die Natur verwendet dieses Prinzip seit Jahrmillionen erfolgreich, auch das Internet wurde so konzipiert (das ARPAnet wurde vom US-Militär für den Einsatz in Kriegsfällen unter massiven Störungen entwickelt). Alle Nostr-Daten liegen auf Relays und der Nutzer kann wählen zwischen öffentlichen (zumeist kostenlosen) und privaten Relays, z.B. für geschlossene Gruppen oder zum Zwecke von Daten-Archivierung. Da Dokumente auf mehreren Relays gespeichert sind, werden statt URL's (Locator) eindeutige Dokumentnamen (URI's = Identifier) verwendet, broken Links sind damit Vergangenheit und Löschungen / Verluste ebenfalls.\ \ Jedes Dokument (Event genannt) wird vom Besitzer signiert, es ist damit authentisch und fälschungssicher und kann nur vom Ersteller gelöscht werden. Dafür wird ein Schlüsselpaar verwendet bestehend aus privatem (nsec) und öffentlichem Schlüssel (npub) wie aus der Mailverschlüsselung (PGP) bekannt. Das repräsentiert eine Nostr-Identität, die um Bild, Namen, Bio und eine lesbare Nostr-Adresse ergänzt werden kann (z.B. roland@pareto.space ), mehr braucht es nicht um alle Ressourcen des Nostr-Ökosystems zu nutzen. Und das besteht inzwischen aus über hundert Apps mit unterschiedlichen Fokussierungen, z.B. für persönliche verschlüsselte Nachrichten (DM → OxChat), Kurznachrichten (Damus, Primal), Blogbeiträge (Pareto), Meetups (Joinstr), Gruppen (Groups), Bilder (Olas), Videos (Amethyst), Audio-Chat (Nostr Nests), Audio-Streams (Tunestr), Video-Streams (Zap.Stream), Marktplätze (Shopstr) u.v.a.m. Die Anmeldung erfolgt mit einem Klick (single sign on) und den Apps stehen ALLE Nutzerdaten zur Verfügung (Profil, Daten, Kontakte, Social Graph → Follower, Bookmarks, Comments, etc.), im Gegensatz zu den fragmentierten Datensilos der Gegenwart.\ \ Resümee: ein offener Standard, alle Daten, alle Rechte = große Zukunft!

\ Warum ist Nostr die Zukunft des Internet?
“Baue Dein Haus nicht auf einem fremden Grundstück” gilt auch im Internet - für alle App-Entwickler, Künstler, Journalisten und Nutzer, denn auch ihre Daten sind werthaltig. Nostr garantiert das Eigentum an den Daten, und überwindet ihre Fragmentierung. Weder die Nutzung noch die kreativen Freiheiten werden durch maßlose Lizenz- und Nutzungsbedingungen eingeschränkt. Aus passiven Nutzern werden durch Interaktion aktive Teilnehmer, Co-Creatoren in einer Sharing-Ökonomie (Value4Value). OpenSource schafft endlich wieder Vertrauen in die Software und ihre Anbieter. Offene Standards ermöglichen den Entwicklern mehr Kooperation und schnellere Entwicklung, für die Anwender garantieren sie Wahlfreiheit. Womit wir letztmalig zu unserem Fünfjährigen zurückkehren. Kinder lieben Lego über alles, am meisten die Maxi-Box “Classic”, weil sie damit ihre Phantasie im Kombinieren voll ausleben können. Erwachsene schenken ihnen dann die viel zu teuren Themenpakete, mit denen man nur eine Lösung nach Anleitung bauen kann. “Was stimmt nur mit meinen Eltern nicht, wann sind die denn falsch abgebogen?" fragt sich der Nachwuchs zu Recht. Das Image lässt sich aber wieder aufpolieren, wenn sie ihren Kindern Nostr zeigen, denn die Vorteile verstehen sogar Fünfjährige.

\ Das neue Internet ist dezentral. Das neue Internet ist selbstbestimmt. Nostr ist das neue Internet.
https://nostr.net/ \ https://start.njump.me/
Hier das Interview zum Thema mit Radio Berliner Morgenröte
-
 @ bf47c19e:c3d2573b
2025-05-11 18:39:10
@ bf47c19e:c3d2573b
2025-05-11 18:39:10Originalni tekst na antenam.net
18.12.2024 / Autor: Ana Nives Radović
Ako ste makar djelić vremena proveli u svijetu digitalnog novca, vjerovatno ste naišli na termin HODL – uvijek napisan velikim slovima tako da na prvi pogled djeluje kao riječ sa slovnom greškom. Zapravo i jeste riječ o slovnoj grešci i to onoj koja je nastala na današnji dan prije 11 godina, a koja je uspjela ne samo da obezbijedi mjesto u istoriji svijeta novca, već i da postane naziv za jedan potpuno drugačiji pristup sredstvima koja posjedujemo.
Nespretno napisana riječ „hold“ (eng. držati, zadržati) u poruci na jednom forumu evoluirala je u akronim HODL – akronim za Hold On for Dear Life (doslovno – drži se za život, tj. drži se kao da ti život zavisi od toga), predstavlja poziv na akciju – ili, tačnije, „neakciju“ za vlasnike kriptovaluta da odole iskušenju prodaje tokom tržišnih padova. Riječ je o shvatanju da je ovaj oblik digitalne imovine bolje vremenski što duže imati u vlasništvu, kako bi se sačekao mnogo povoljniji trenutak za prodaju nego prodati ih u vremenu kada je situacija na tržištu loša.
Greška koja je postala pokret
Priča počinje 18. decembra 2013. godine, kada je cijena bitcoina tada počela da pada, a samo tokom toga dana se sa 682 na 522 dolara. Korisnik foruma pod imenom GameKyuubi objavio je sada već legendarni post pod naslovom „I AM HODLING“. Bila je to greška u kucanju, jer se na osnovu sadržaja poruke vidi da je krenuo da napiše „holding“ (držim), ali umjesto da se ispravi sebe, prigrlio je grešku, šaljivo govoreći o svom nedostatku vještina za trgovanje i zašto „bez obzira na sve“.

Bitcoin zajednica brzo je prihvatila ovaj izraz kao dio slenga. Pogrešno napisana riječ odjeknula je internet prostranstvima, a vremenom je prerasla u simbol šire filozofije – ne paniči, ne prodaj i ne dozvoli da kratkoročna nestabilnost poljulja tvoje uvjerenje. Od kasnonoćnog posta na forumu, HODL je postao poklič za vlasnike bitcoina (i drugih, u to vrijeme malobrojnih digitalnih valuta zanemarive vrijednosti) širom svijeta.
HODL-ovanje i HODL-eri
U suštini, HODL-ovanje je strategija zadržavanja kriptovaluta tokom tržišnih uspona i padova, zasnovana na uvjerenju da će cijene vremenom rasti. Umjesto impulsivnog reagovanja na tržišne fluktuacije, HODL-eri se posvećuju svojim investicijama na duže staze.
Ovaj pristup posebno je koristan za početnike, koji možda nemaju dovoljno stručnosti ili hrabrosti da se nose sa svakodnevnim trgovanjem (u čemu su često neuspješni i dugogodišnji vlasnici digitalnih novčića). Sam GameKyuubi u svom originalnom postu priznao je da samo najvještiji trgovci treba da pokušaju da „igraju igru“ tokom tržišnih padova. Za ostale, HODL-ovanje nije samo sigurnije, već je često i pametnije.
Filozofija HODL-ovanja zasnovana je na povjerenju – u budućnost kriptovaluta, u eventualni oporavak tržišta i u korist koju donosi strpljenje. To je odbijanje da se prodaje kada cijene naglo padnu – nepokolebljivo uvjerenje da su padovi privremeni i da nakon njih slijedi rast.
Zakon tržišta pokazuje da što drže HODL-ujete to se ova strategija više isplati, a cijena bitcoina u njegovoj šesnaestogodišnjoj istoriji je nesumnjivo najbolji dokaz za to. Trgovanje zahtijeva mnogo učenja, truda, vremena provedenog u praćenju svakog mogućeg signala, dok je kod HODL-ovanja važno samo da se „ne predate“.
Ako ste prethodnih godina nešto platili bitcoinom (a trgovci širom svijeta su to omogućili upravo da bi vas naveli da ih umjerite ka njima) vjerovatno ste zažalili, jer danas dok je njegova vrijednost i u dolarima i u eurima šestocifrena, ono na što ste ih potrošili ipak izgleda kao nešto što je trebalo platiti fizičkim novcem (kojeg je svakako „pojela inflacija“).
Pouzdane kriptovalute, a tu se prije svega misli na bitcoin, iako veoma volatilne bilježe trend rasta na duge staze, pa HODL-ovanje znači strpljenje u vremenu neizvjesnosti s idejom o koristi na duži rok, čak i kada su godine loše, kao što su bile 2014, 2017. i 2022. Na primjer, u periodu od 20. maja do 20. juna cijena bitcoina kliznula je sa 29.000 na 18.000 dolara, a upravo u tom trenutku mnogi su odlučili da količinu koju posjeduju prodaju ili je potroše plaćajući ovom digitalnom valutom (i pokajali se zbog toga).
HODL naspram drugih strategija
HODL-ovanje se razlikuje od aktivnijih strategija, poput kupovine po niskoj cijeni i prodaje po visokoj, jer dok trgovci pokušavaju da tempiraju tržište radi brze zarade, HODL-eri ostaju dosljedni svojoj odluci da se ne oslobađaju svoje imovine ni u najnoepovoljnijim trenucima. HODL-eri ne pokušavaju da predvide kretanje cijena – jednostavno čuvaju svoja sredstva, svjesni toga da će strpljenje na kraju donijeti rezultat.
Naravno, HODL-ovanje ima i svoje nedostatke. Za razliku od trgovaca koji mogu da povećaju svoj kapital kroz stratešku kupovinu i prodaju, HODL-eri zavise od vremena provedenog u čekanju na dugoročne rezultate. Pored toga, masovno HODL-ovanje može usporiti cirkulaciju kriptovaluta na tržištu, smanjujući ukupnu ekonomsku aktivnost – drugim riječima, kada bismo svi bili HODL-eri odnos ponude i tražnje bi bio veoma destimulišući i to bi oborilo cijenu.
Na sreću, trgovaca ima mnogo – dovoljno da tržište stalno bude aktivno i dinamično, no za one koji nemaju vremena, vještine ili sklonost ka riziku koji nosi trgovanje, HODL-ovanje ostaje jednostavan, ali veoma efikasan pristup.
Filozofija HODL-ovanja
HODL-ovanje je više od investicione strategije – to je način razmišljanja koji obuhvata otpornost, strpljenje i vjerovanje da su kratkotrajno suzdržavanje i nepokolebljivost u odluci da se sredstva sačuvaju vrijedna dugoročnog dobitka. Bilo da cijena bitcoina raste ili pada je, filozofija HODL-ovanja ostaje ista – ostanimo dosljedni, vjerujmo procesu i gledajmo u budućnost.
Jedan od ključnih razloga zašto većini ljudi ovakav pristup dugo nije bio razumljiv je zbog toga što su čitav sistem novca prihvatili u uvjerenju da on vremenom devalvira. Vjerovatno ste makar jednom razmatrali ponudu oročene štednje i procijenili da vam količina novca koju želite da položite neće donijeti onaj prinos koji će očuvati njegovu kupovnu moć nakon određenog broja godina, jer je kontinuirano doštampavanje novca podupiralo tu tvrdnju.
Dakle, ne treba da vas zavara sve ono što znate o novcu kao takvom, budući da bitcoin (na kojem je u ovom serijalu poseban fokus, jer mnoge druge kriptovalute ipak češće razočaraju nego što oduševe) nije novac, već samo ima neka svojstva novca. Posmatrajte ga radije kao imovinu – npr. kao nekretninu za koju sigurno želite da prodate onda kada je situacija stabilnija i kada su mnogo veće šanse da pronađete kupca kojem ćete je prodati po višoj cijeni.
U svakom slučaju, ako se u vašem digitalnom novčaniku već nalazi poneki satoshi (stomilioniti djelić bitcoina), kada tržište ponovo uđe u nepovoljnu fazu i zavlada prolazna panika, sjetite se onoga što je napisao GameKyuubi. HODL nije samo izraz – to je način da se prebrode oluje i izazovi koje nestabilno tržište nosi.
-
 @ bf47c19e:c3d2573b
2025-05-11 18:37:13
@ bf47c19e:c3d2573b
2025-05-11 18:37:13Apstrakt
Kriptovalute (engl. "cryptocurrency") su digitalne (virtualne) valute, koje iako su sredstvo razmene, još uvek nisu strogo regulisane zakonom u većini država, a u pojedinim su čak i zabranjene. Veliki broj ljudi, uključujući i IT stručnjake i programere ne znaju mnogo o ovoj temi, a šira javnost izjednačava pojmove blokčejna i bitkoina. Tržište kriptovaluta danas iznosi gotovo 770 milijardi dolara. Od pojave prvih digitalnih valuta do danas, nastalo je preko 1.300 aktivnih kriptovaluta koje se razlikuju prema svojim svojstvima i upotrebi. Pre bitkoina bilo je mnoštvo neuspelih pokušaja stvaranja digitalnih valuta (digikeš, heškeš, Fejsbuk kredit i dr.). Utopistička ideja da matematika i fizika mogu rešiti društvene probleme započela je svoj život kroz pojavu bitkoina. Genijalna ideja po kojoj funkcioniše bitkoin zasnovana je na tehnologiji blokčejna, čiji kapacitet doseže daleko iznad kripto valuta. Iako se još uvek vode polemike ko stoji iza pseudonima Satoši Nakamoto, njegova zaostavština ima potencijal da promeni svet. Uspeh bitkoina leži u prednostima koje ima u odnosu na druge slične valute, ali njegov značaj prevazilazi i pogodnosti koje je doneo. Banke nisu potrebne za čuvanje podataka o novcu, evidenciju o imovini i svakoj transakciji bitkoina čuvaju računari svih korisnika mreže u zajedničkoj bazi podataka blokčejnu. Sve transakcije su mnogo brže od bankarskih, bez taksi, uz drastično lakše plaćanje preko državnih granica. Bitkoin svojim korisnicima pruža bezbednosti bez identifikacije, iako blokčejn beleži transakciju, ne beleži ko stoji iza nje. U radu su predstavljeni osnovni principi na kojima su zasnovani bitkoin i druge kriptovalute, pojašnjen odnos između blokčejna i bitkoina.
1 UVOD
Ideal o novcu koji se ne oslanja na centralne institucije (koje mogu propasti, ali i koje vrše nadzor nad korisnicima), postojao je decenijama. U digitalnom svetu prvi ga je uobličio pisac naučne fantastike Nil Stivenson 1999. godine u svojoj noveli Kriptonomikon. On je opisao podzemni svet koji funkcioniše zahvaljujući digitalnom zlatu zasnovanom na kriptografiji, pri čijoj upotrebi korisnici ne moraju odavati ko su i šta su (Popper, 2016).
Kriptovalute (engl. cryptocurrency) su digitalne (virtualne) valute, koje iako su sredstvo razmene, još uvek nisu strogo regulisane zakonom u većini država, a u pojedinim su čak i zabranjene (Jovanović, 2014).
Da bi se razumeo nastanak i funkcionisanje kriptovaluta, neophodno je sagledati ih iz različitih uglova na kojima su one bazirane: matematici, sociologiji, ekonomiji, pravu i politici. To je verovatno i glavni razlog zbog koga veliki broj ljudi (uključujući i IT stručnjake i programere) ne znaju mnogo o ovoj temi. Takođe, šira javnost izjednačava pojmove blokčejna i bitkoina.
Sve kriptovalute su bazirane na jedinstvenom nizu brojeva za svaku jedinicu valute, koje korisnici mogu jedni drugima slati preko mreže. U prošlosti su se ti nizovi mogli lako kopirati i trošiti više puta, zbog čega nisu imali vrednost. Kriptograf Dejvid Čaum je taj problem rešio stvaranjem jedinstvene centralizovane knjige, u kojoj su se čuvale beleške o transakcijama svakog korisnika, čime ni jedna jedinica valute više nije mogla da se nalazi na dva mesta istovremeno (Bertlet, 2016).
Kriptovalute svoj nastanak duguju težnjama levo orijentisanih utopističkih posvećenika IT tehnologija koji su sanjali o univerzalnom novcu koji bi svako mogao da poseduje i troši, čija je vrednost onolika koliko su korisnici voljni da plate (na principu ponude i potražnje), ali pre svega na liniji fronta za onlajn anonimnost i slobodu, bez cenzure i nadzora. Pojavi bitkoina prethodio je Sajberpankerski manifest Done Haravej (Haraway, 1985) koji počinje rečima: „U elektronsko doba, privatnost je neophodan uslov za postojanje otvorenog društva“.
Kriptovalute su univerzalni novac koji se može koristiiti bilo gde u svetu, one su lako prenosive i teško se krivotvore.
Neki podaci pokazuju da tržište kriptovaluta danas iznosi gotovo 770 milijardi dolara. Od pojave prvih digitalnih valuta do danas, nastalo je preko 1.300 aktivnih kriptovaluta koje se razlikuju prema svojim svojstvima i upotrebi.
Prema odredbama Zakona o Narodnoj banci Srbije celokupni unutrašnji promet u Republici Srbiji izražava se u dinarima, osim ako nekim zakonom nije drukčije određeno. „Zakonom o platnom prometu propisano je da se poslovi platnog prometa obavljaju u dinarima, a Zakonom o deviznom poslovanju da se plaćanje, naplaćivanje i prenos između rezidenata i između rezidenata i nerezidenata u Republici Srbiji vrši u dinarima, a izuzetno se može vršiti i u devizama u slučajevima koji su propisani ovim zakonom“ (NBS, 2014).
Tržište kriptovaluta u Srbiji postoji, sve je veći broj rudara. Iako trgovanje kriptovalutama nije nelegalno, Narodna Banka Srbije - NBS je u više saopštenja navela da one ne predstavljaju zakonsko sredstvo plaćanja u Republici Srbiji. Takođe, zbog toga što ih ne izdaje centralna banka, NBS za korišćenje virtuelnih valuta, ulaganje u njih, kao ni za njihovu vrednost. Narodna banka Srbije je više puta upozoravala javnost da virtuelne valute ne predstavljaju zakonsko sredstvo plaćanja u Republici Srbiji (NBS, Politika – u vezi s bitkoinom, 2017).
Ukoliko kriptovalute promatramo kao novac onda njihove tranksakcije mogu biti upitne shodno Zakonu o sprečavanju pranja novca i finansiranja terorizma, gde je propisana obaveza preduzimanja radnji i mera za sprečavanje pranja novca, kao što su identifikacija stranaka koje trguju preko tih platformi, uzimanjem kopije ličnog dokumenta. Kako poslovanje platformi na kojima se vrše transakcije kriptovalutama nije zakonom regulisano u Republici Srbiji, a uglavnom ni u uporednom pravu, a čl. 552. Zakona o obligacionim odnosima Republike Srbije ((„Sl. list SFRJ“, br. 29/78, 39/85, 45/89 - odluka USJ i 57/89, „Sl. list SRJ“, br. 31/93 i „Sl. list SCG“, br. 1/2003 - Ustavna povelja) predviđa razmenu robe kao jedan od načina trgovine, otvara se put ka legalnoj trgovini kriptovalutama (Bubanja, 2017).
Praksa je pokazala da su se korisnici kriptovaluta kada su imali problem sa njima, obraćali vlastima i njihovim regulatornim telima, zbog čijeg su zaobilaženja i smišljeni. Nažalost, korisnici ne uživaju pravnu zaštitu čak i kada je reč o trgovini putem registrovanih privrednih subjekta.
2 BITKOIN
Prva decentralizovana kriptovaluta koja se pojavila je bitkoin (eng. „Bitcoin“). Termin bitkoin označava istoimenu organizaciju, softver i protokol, kao i jedinicu mere ove kriptovalute (skraćeno BTC) (Bertlet, 2016). Koncept na kome se zasniva bitkoin prvi put je predstavljen 2008. godine u članku "Bitcoin: A Peerto-Peer Electronic Cash System", a u januaru 2009. godine bitkoin je pušten u promet. Njegov tvorac nije poznat do danas i krije se iza pseudonima Satoši Nakomato. Novu vrstu digitalne kriptovalute formirao je tako što je stvorio distribuirani sistem verifikacije. Bitkoin nastaje u procesu koji se naziva „rudarenje“ (engl. mining). Njegova jedinstvenost je u tome što je decentralizovana valuta, iza koje ne stoji nijedna država, niti banka. Bitkoin je digitalna valuta, koja nastaje i čuva se elektronski. Kriptovalute u cilju maksimizacije bezbednosti, upotrebljavaju metod - dokaz o radu (engl. proofof-work), metod baziran na informacijama koje je teško stvoriti, ali koje ostalim učesnicima u rudarenju obezbeđuju laku proveru i verifikaciju transakcija.
Kriptovalute se čuvaju na bitkoin adresama za koje ključ predstavlja jedinstven niz slova i brojeva. Svaka transkacija bitkoinom se beleži u blokovima koji se zovu blokčejn. Transakcije se hronološki ređaju u blokove, u svakom se nalazi digitalni potpis prethodnog bloka, time se uređuje redosled i garantuje da novi blok može da se pridruži lancu samo ako počne na mestu na mestu završetka prethodnog. Jedan od osnovnih činilaca bezbednosti bitkoina je da se kopija svake izvedene transakcije beleži na svakom nalogu na kome je instaliran bitkoin softver. Blokčejnove neprekidno verifikuju računari svih korisnika softvera, tako sistem zna u bilo kom trenutku, koliko bitkoina svaki korisnik u svom novčaniku poseduje. Novčanik je program koji služi za slanje, primanje i skladištenje kriptovaluta. Digitalni novčanik sadrži prikaz količine kriptovalute koju korisnik poseduje, zapise o svim njegovim transakcijama, korisnički tajni ključ i njegove adrese (Bertlet, 2016). Novčanik je moguće instalirati na računar, mobilni telefon i tablet.
Falsifikovanje bitkoina nije moguće, jer iako vlasništvo može da se menja ono se ne može nikada duplirati (Bertlet, 2016). On je pseudoanoniman, bitkoin mreža čuva sve podatke o svakoj transakciji koja se dogodila unutar mreže. Svako ko ima bitkoin softver i adresu na bitkoin mreži, može videti koliko novca ima na mreži, ali ne i kome oni pripadaju. Za razliku od otvaranja računa u bankama, otvaranje bitkoin računa (adrese) je brzo, bez troškova i „papirologije“. Jedna od glavnih prednosti bitkoin mreže je brzina transakcija.
Svako ko snagu svog računara posveti verifikaciji transakcija u blokčejnu može biti „rudar“. To je proces dodavanja transkacija u registar svih bitkoin transkacija. Rudarenje čini rešavanje matematičkog algoritma za čije se uspešno rešavanje dobija određena količina bitkoina.
Iako bitkoin ima reputaciju nestabilnosti, velikih fluktuacija i nezakonitog poslovanja, čemu mnogi pridodaju i urušavanje tradicionalnog koncepta nacionalnih država, ipak većina se slaže u tome da je njegova pojava najvažnija nova ideja od stvaranja Interneta (Vigna & Casey, 2016).
Razloga za uspeh bitkoina ima više. Finansijska kriza povoljno je uticala na njegov razvoj, poverenje u postojeći finansijski ali i politički sistem je bilo poljuljano i brojni korisnici su u njemu prepoznali drugačije rešenje.
Anonimnost koju pruža prilikom transakcija jedan je od ključnih razloga njegovog uspeha. Prilikom digitalnog plaćanja bitkoinom u većini slučajeva nije potrebno davanje ličnih podataka. Ovakva vrsta anonimnosti, nažalost pogodovala je i usponu tamne strane upotrebe i popularnosti bitkoina u kriminalnim krugovima.
Računi u bitkoinu nisu opterećeni visokim bankarskim dažbinama.
Takođe, nije beznačajan ni potencijal plaćanja izdataka koji su manji od trenutnih ograničenja u konvencijalnim transakcijama na internetu (npr. naplata čitanja jednog novinskog članka ili preskoči reklamu, koji koštaju manje od 20 ili 30 centi kolika je najmanja transakcija) (Popper, 2016).
Kao što su svi učesnici na internetu povezani protokolima (TCP/IP, FTP, SMTP, HTTP i dr.) zahvaljujući kojima mogu međusobno da komuniciraju, bitkoin je stvorio svoje softverske protokole koji uređuju funkcionalna pravila upravljanja sistemom.
Bitkoin je omogućio novi način stvaranja, čuvanja i transfera novca.
Od svog nastanka bitkoin se unapređivao, podržan od internet zajednice, posebno od posvećenika slobodi interneta i anonimosti, mnogi od problema koji su uočeni su rešavani zajedničkim naporom internet zajednice.
3 BLOKČEJN
Blokčejn (engl. blockchain) nije samo bitkoin, on je tehnologija za koju mnogi predviđaju da će promeni svet (OECD, 2018).
Ukoliko bismo pojednostavljeno opisivali blokčejn mogli bismo da kažemo da je to nova vrsta baze podataka, iako bi to bilo pojednostavljeno objašnjenje slično kao kada bi smo imejl (email) opisali kao novi način za slanje pisama.
Iako blokčejn jeste nova vrsta baze podatka, to ne objašnjava u dovoljnoj meri genijalnost načina na koji funkcioniše.
Kada bilo gde i bilo kada položimo novac, oslanjamo se na zapis u bazi podataka treće strane, banke, firme i sl. Poverenje u banke zasnovano je na zakonu koji reguliše rad banke, poverenju u državu da će u slučaju propasti banke država nadoknaditi klijentima njihov ulog.
Kada plaćamo on line usluge ili vršimo neku drugu transakciju kreditnim karticama, poklanjamo poverenje kompanijama koje posreduju u našem plaćanju (Mastercard, VISA i dr.) koje za to uzimaju određenu materijalnu nadoknadu. Čak i prilikom tradicionalnih oblika plaćanja gotovinom u papirnom novcu, mi dajemo papir na kome je ispisana vrednost za koju prodavac veruje da će mu biti isplaćena (ili garantovana) od strane vlade koja ju je štampala. Digitalno plaćanje zbog prisustva trećih strana (banke, kreditne kompanije i dr.) uvek je bilo moguće pratiti. I kod plaćanja gotovinom klijenti veruju bankama i kreditnim kompanijama koje rukovode platnim karticama, da imaju pouzdane baze podataka. I vlade država veruju da banke i kreditne kompanije vode baze podataka koje su tačne i pouzdane.
Baze podataka sadrže mnoštvo ličnih podataka, od npr. medicinske dokumentacije u domu zdravlja koja sadrži važne informacije o nama i našem zdravstvenom stanju, kada smo i od koje bolesti bolovali, koje lekove smo koristili i sl. I druge baze podataka sadrže mnoštvo naših ličnih podataka koje su važne ne samo za nas, već i za državu, grad, privredu, druge građane itd.
Osim što omogućava anonimne i sigurne transakcije, blokčejn ima i potencijal da sačuva sve vredne informacije, od podataka o rođenim i umrlim, preko osiguranja, do katastara nepokretnosti, pa čak i glasova (Tapscott, 2018).
Sagledavši mogućnosti koji blokčejn nudi u transformaciji industrija i tržišta, povećanju transparentnosti i poverenja između građana, kao i olakšanom pristupu tržištu (uz bolju efikasnost transakcija), ali i rizicima koje sa sobom nosi, Organizacija za ekonomsku saradnju i razvoj - OECD organizovala je od 4. do 5. septembra 2018. godine Forum politike OECD-a za blokčejn. To je bila ujedno i prva glavna međunarodna konferencija na kojoj se razmatrao uticaj blokčejna na aktivnosti vlada i javnih prioriteta. Forum se bavio prednostima i rizicima blokčejna za ekonomiju i društvo, pokušajem određivanja adekvatnog regulatornog pristupa, kao i javnih politika prema blokčejnu.
Učesnici Foruma su diskutovali o mogućnostima globalnog ekonomskog uticaja blokčejna, njegovim implikacijama na privatnost i sajber bezbednost, upotrebi blokčejn tehnologija za povećanje inkluzivnosti, njegovoj upotrebi u promovisanju zelenog rasta i održivosti, kao i jačanju kapaciteta javne uprava i primene u praksi (OECD, 2018).
4 ZAKLJUČAK
Pre bitkoina bilo je mnoštvo neuspelih pokušaja stvaranja digitalnih valuta (digikeš, heškeš, Fejsbuk kredit i dr.). Uspeh bitkoina leži u prednostima koje ima u odnosu na druge slične valute, ali njegov značaj prevazilazi i pogodnosti koje je doneo.
Svaki korisnik bitkoina ima potpunu kontrolu nad novcem na svom računu (adresi), jedino osoba sa privatnim ključem može pristupiti bitkoinima na toj adresi. Banke nisu potrebne za čuvanje podataka o novcu, evidenciju o imovini i svakoj transakciji bitkoina čuvaju računari svih korisnika mreže u zajedničkoj bazi podataka blokčejnu. Sve transakcije su mnogo brže od bankarskih, bez taksi, uz drastično lakše plaćanje preko državnih granica.
Bitkoin svojim korisnicima pruža bezbednosti bez identifikacije, iako blokčejn beleži transakciju, ne beleži ko stoji iza nje. Zahvaljujući peer-to-peer komunikaciji i kriptografiji, povezivanje bitkoin transakcija sa osobom u stvarnom životu je veoma teško. To je u ujedno možda i njegova najveća mana, jer su oporezivanje i nadzor nad korisnicima krajnje teški.
Garancija vrednosti bitkoina osmišljena je po uzoru na plamenite metale kojih ima ograničeno u prirodi. Zbog toga je Satoši u kodu bitkoina odredio da ih ima maksimalno 21 milion, te da ukoliko bitkoin protokol ostane isti, poslednji bitkoin će biti izrudaren 2140. godine.
Do sada je izrudareno oko 17 miliona bitkoina, što znači da je ostalo 4 miliona, ili oko 19%. Do sada je bitkoin uspeo da prevlada sve krize koje su ga zahvatile (u više slučajeva nestajali su iznosi koji su dostizali i 400 miliona dolara). Kakva god sudbina bitkoina bila u budućnosti, njegova uloga se neće moći zanemariti, prvenstveno zbog toga što je zahvaljujući njemu iznedren blokčejn. Bez obzira na skepticima u vezi sa kriptovalutama, teško se mogu osporiti mogućnosti koje blokčejn pruža, pre svega u zaštiti baza podatka.
-
 @ 9e69e420:d12360c2
2025-01-19 04:48:31
@ 9e69e420:d12360c2
2025-01-19 04:48:31A new report from the National Sports Shooting Foundation (NSSF) shows that civilian firearm possession exceeded 490 million in 2022. The total from 1990 to 2022 is estimated at 491.3 million firearms. In 2022, over ten million firearms were domestically produced, leading to a total of 16,045,911 firearms available in the U.S. market.
Of these, 9,873,136 were handguns, 4,195,192 were rifles, and 1,977,583 were shotguns. Handgun availability aligns with the concealed carry and self-defense market, as all states allow concealed carry, with 29 having constitutional carry laws.
-
 @ f9cf4e94:96abc355
2025-01-18 06:09:50
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |
 | Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |
| Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |  | 16Gb |
| 16Gb |Recomendo que use o Ubuntu Server para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi aqui. O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível aqui. Não instale um desktop (como xubuntu, lubuntu, xfce, etc.).
Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
bash apt update apt install tor
Passo 2: Criar o Arquivo de Serviço
nrs.service🔧Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit [Unit] Description=Nostr Relay Server Service After=network.target
[Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure
[Install] WantedBy=multi-user.target ```
Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr aqui no GitHub.
Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
bash mkdir -p /opt/nrs /mnt/edriver
Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
bash lsblk
Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo,
/dev/sda) e formate-o:bash mkfs.vfat /dev/sda
Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta
/mnt/edriver:bash mount /dev/sda /mnt/edriver
Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
bash blkid
Passo 9: Alterar o
fstabpara Montar o Pendrive Automáticamente 📝Abra o arquivo
/etc/fstabe adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta
/opt/nrs:bash cp nrs-arm64 /opt/nrs
Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em
/opt/nrs/config.yaml:yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true
Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo
nrs.servicepara o diretório/etc/systemd/system/:bash cp nrs.service /etc/systemd/system/Recarregue os serviços e inicie o serviço
nrs:bash systemctl daemon-reload systemctl enable --now nrs.service
Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor
/var/lib/tor/torrce adicione a seguinte linha:torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334
Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
bash systemctl enable --now tor.serviceO Tor irá gerar um endereço
.onionpara o seu servidor Nostr. Você pode encontrá-lo no arquivo/var/lib/tor/nostr_server/hostname.
Observações ⚠️
- Com essa configuração, os dados serão salvos no pendrive, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço
.oniondo seu servidor Nostr será algo como:ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion.
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-
 @ 6389be64:ef439d32
2025-01-16 15:44:06
@ 6389be64:ef439d32
2025-01-16 15:44:06Black Locust can grow up to 170 ft tall
Grows 3-4 ft. per year
Native to North America
Cold hardy in zones 3 to 8

Firewood
- BLT wood, on a pound for pound basis is roughly half that of Anthracite Coal
- Since its growth is fast, firewood can be plentiful
Timber

- Rot resistant due to a naturally produced robinin in the wood
- 100 year life span in full soil contact! (better than cedar performance)
- Fence posts
- Outdoor furniture
- Outdoor decking
- Sustainable due to its fast growth and spread
- Can be coppiced (cut to the ground)
- Can be pollarded (cut above ground)
- Its dense wood makes durable tool handles, boxes (tool), and furniture
- The wood is tougher than hickory, which is tougher than hard maple, which is tougher than oak.
- A very low rate of expansion and contraction
- Hardwood flooring
- The highest tensile beam strength of any American tree
- The wood is beautiful
Legume
- Nitrogen fixer
- Fixes the same amount of nitrogen per acre as is needed for 200-bushel/acre corn
- Black walnuts inter-planted with locust as “nurse” trees were shown to rapidly increase their growth [[Clark, Paul M., and Robert D. Williams. (1978) Black walnut growth increased when interplanted with nitrogen-fixing shrubs and trees. Proceedings of the Indiana Academy of Science, vol. 88, pp. 88-91.]]
Bees

- The edible flower clusters are also a top food source for honey bees
Shade Provider

- Its light, airy overstory provides dappled shade
- Planted on the west side of a garden it provides relief during the hottest part of the day
- (nitrogen provider)
- Planted on the west side of a house, its quick growth soon shades that side from the sun
Wind-break

- Fast growth plus it's feathery foliage reduces wind for animals, crops, and shelters
Fodder
- Over 20% crude protein
- 4.1 kcal/g of energy
- Baertsche, S.R, M.T. Yokoyama, and J.W. Hanover (1986) Short rotation, hardwood tree biomass as potential ruminant feed-chemical composition, nylon bag ruminal degradation and ensilement of selected species. J. Animal Sci. 63 2028-2043
-
 @ 6389be64:ef439d32
2025-01-14 01:31:12
@ 6389be64:ef439d32
2025-01-14 01:31:12Bitcoin is more than money, more than an asset, and more than a store of value. Bitcoin is a Prime Mover, an enabler and it ignites imaginations. It certainly fueled an idea in my mind. The idea integrates sensors, computational prowess, actuated machinery, power conversion, and electronic communications to form an autonomous, machined creature roaming forests and harvesting the most widespread and least energy-dense fuel source available. I call it the Forest Walker and it eats wood, and mines Bitcoin.
I know what you're thinking. Why not just put Bitcoin mining rigs where they belong: in a hosted facility sporting electricity from energy-dense fuels like natural gas, climate-controlled with excellent data piping in and out? Why go to all the trouble building a robot that digests wood creating flammable gasses fueling an engine to run a generator powering Bitcoin miners? It's all about synergy.
Bitcoin mining enables the realization of multiple, seemingly unrelated, yet useful activities. Activities considered un-profitable if not for Bitcoin as the Prime Mover. This is much more than simply mining the greatest asset ever conceived by humankind. It’s about the power of synergy, which Bitcoin plays only one of many roles. The synergy created by this system can stabilize forests' fire ecology while generating multiple income streams. That’s the realistic goal here and requires a brief history of American Forest management before continuing.
Smokey The Bear
In 1944, the Smokey Bear Wildfire Prevention Campaign began in the United States. “Only YOU can prevent forest fires” remains the refrain of the Ad Council’s longest running campaign. The Ad Council is a U.S. non-profit set up by the American Association of Advertising Agencies and the Association of National Advertisers in 1942. It would seem that the U.S. Department of the Interior was concerned about pesky forest fires and wanted them to stop. So, alongside a national policy of extreme fire suppression they enlisted the entire U.S. population to get onboard via the Ad Council and it worked. Forest fires were almost obliterated and everyone was happy, right? Wrong.
Smokey is a fantastically successful bear so forest fires became so few for so long that the fuel load - dead wood - in forests has become very heavy. So heavy that when a fire happens (and they always happen) it destroys everything in its path because the more fuel there is the hotter that fire becomes. Trees, bushes, shrubs, and all other plant life cannot escape destruction (not to mention homes and businesses). The soil microbiology doesn’t escape either as it is burned away even in deeper soils. To add insult to injury, hydrophobic waxy residues condense on the soil surface, forcing water to travel over the ground rather than through it eroding forest soils. Good job, Smokey. Well done, Sir!
Most terrestrial ecologies are “fire ecologies”. Fire is a part of these systems’ fuel load and pest management. Before we pretended to “manage” millions of acres of forest, fires raged over the world, rarely damaging forests. The fuel load was always too light to generate fires hot enough to moonscape mountainsides. Fires simply burned off the minor amounts of fuel accumulated since the fire before. The lighter heat, smoke, and other combustion gasses suppressed pests, keeping them in check and the smoke condensed into a plant growth accelerant called wood vinegar, not a waxy cap on the soil. These fires also cleared out weak undergrowth, cycled minerals, and thinned the forest canopy, allowing sunlight to penetrate to the forest floor. Without a fire’s heat, many pine tree species can’t sow their seed. The heat is required to open the cones (the seed bearing structure) of Spruce, Cypress, Sequoia, Jack Pine, Lodgepole Pine and many more. Without fire forests can’t have babies. The idea was to protect the forests, and it isn't working.
So, in a world of fire, what does an ally look like and what does it do?
Meet The Forest Walker

For the Forest Walker to work as a mobile, autonomous unit, a solid platform that can carry several hundred pounds is required. It so happens this chassis already exists but shelved.
Introducing the Legged Squad Support System (LS3). A joint project between Boston Dynamics, DARPA, and the United States Marine Corps, the quadrupedal robot is the size of a cow, can carry 400 pounds (180 kg) of equipment, negotiate challenging terrain, and operate for 24 hours before needing to refuel. Yes, it had an engine. Abandoned in 2015, the thing was too noisy for military deployment and maintenance "under fire" is never a high-quality idea. However, we can rebuild it to act as a platform for the Forest Walker; albeit with serious alterations. It would need to be bigger, probably. Carry more weight? Definitely. Maybe replace structural metal with carbon fiber and redesign much as 3D printable parts for more effective maintenance.
The original system has a top operational speed of 8 miles per hour. For our purposes, it only needs to move about as fast as a grazing ruminant. Without the hammering vibrations of galloping into battle, shocks of exploding mortars, and drunken soldiers playing "Wrangler of Steel Machines", time between failures should be much longer and the overall energy consumption much lower. The LS3 is a solid platform to build upon. Now it just needs to be pulled out of the mothballs, and completely refitted with outboard equipment.
The Small Branch Chipper

When I say “Forest fuel load” I mean the dead, carbon containing litter on the forest floor. Duff (leaves), fine-woody debris (small branches), and coarse woody debris (logs) are the fuel that feeds forest fires. Walk through any forest in the United States today and you will see quite a lot of these materials. Too much, as I have described. Some of these fuel loads can be 8 tons per acre in pine and hardwood forests and up to 16 tons per acre at active logging sites. That’s some big wood and the more that collects, the more combustible danger to the forest it represents. It also provides a technically unlimited fuel supply for the Forest Walker system.
The problem is that this detritus has to be chewed into pieces that are easily ingestible by the system for the gasification process (we’ll get to that step in a minute). What we need is a wood chipper attached to the chassis (the LS3); its “mouth”.
A small wood chipper handling material up to 2.5 - 3.0 inches (6.3 - 7.6 cm) in diameter would eliminate a substantial amount of fuel. There is no reason for Forest Walker to remove fallen trees. It wouldn’t have to in order to make a real difference. It need only identify appropriately sized branches and grab them. Once loaded into the chipper’s intake hopper for further processing, the beast can immediately look for more “food”. This is essentially kindling that would help ignite larger logs. If it’s all consumed by Forest Walker, then it’s not present to promote an aggravated conflagration.
I have glossed over an obvious question: How does Forest Walker see and identify branches and such? LiDaR (Light Detection and Ranging) attached to Forest Walker images the local area and feed those data to onboard computers for processing. Maybe AI plays a role. Maybe simple machine learning can do the trick. One thing is for certain: being able to identify a stick and cause robotic appendages to pick it up is not impossible.
Great! We now have a quadrupedal robot autonomously identifying and “eating” dead branches and other light, combustible materials. Whilst strolling through the forest, depleting future fires of combustibles, Forest Walker has already performed a major function of this system: making the forest safer. It's time to convert this low-density fuel into a high-density fuel Forest Walker can leverage. Enter the gasification process.
The Gassifier

The gasifier is the heart of the entire system; it’s where low-density fuel becomes the high-density fuel that powers the entire system. Biochar and wood vinegar are process wastes and I’ll discuss why both are powerful soil amendments in a moment, but first, what’s gasification?
Reacting shredded carbonaceous material at high temperatures in a low or no oxygen environment converts the biomass into biochar, wood vinegar, heat, and Synthesis Gas (Syngas). Syngas consists primarily of hydrogen, carbon monoxide, and methane. All of which are extremely useful fuels in a gaseous state. Part of this gas is used to heat the input biomass and keep the reaction temperature constant while the internal combustion engine that drives the generator to produce electrical power consumes the rest.
Critically, this gasification process is “continuous feed”. Forest Walker must intake biomass from the chipper, process it to fuel, and dump the waste (CO2, heat, biochar, and wood vinegar) continuously. It cannot stop. Everything about this system depends upon this continual grazing, digestion, and excretion of wastes just as a ruminal does. And, like a ruminant, all waste products enhance the local environment.
When I first heard of gasification, I didn’t believe that it was real. Running an electric generator from burning wood seemed more akin to “conspiracy fantasy” than science. Not only is gasification real, it’s ancient technology. A man named Dean Clayton first started experiments on gasification in 1699 and in 1901 gasification was used to power a vehicle. By the end of World War II, there were 500,000 Syngas powered vehicles in Germany alone because of fossil fuel rationing during the war. The global gasification market was $480 billion in 2022 and projected to be as much as $700 billion by 2030 (Vantage Market Research). Gasification technology is the best choice to power the Forest Walker because it’s self-contained and we want its waste products.
Biochar: The Waste

Biochar (AKA agricultural charcoal) is fairly simple: it’s almost pure, solid carbon that resembles charcoal. Its porous nature packs large surface areas into small, 3 dimensional nuggets. Devoid of most other chemistry, like hydrocarbons (methane) and ash (minerals), biochar is extremely lightweight. Do not confuse it with the charcoal you buy for your grill. Biochar doesn’t make good grilling charcoal because it would burn too rapidly as it does not contain the multitude of flammable components that charcoal does. Biochar has several other good use cases. Water filtration, water retention, nutrient retention, providing habitat for microscopic soil organisms, and carbon sequestration are the main ones that we are concerned with here.
Carbon has an amazing ability to adsorb (substances stick to and accumulate on the surface of an object) manifold chemistries. Water, nutrients, and pollutants tightly bind to carbon in this format. So, biochar makes a respectable filter and acts as a “battery” of water and nutrients in soils. Biochar adsorbs and holds on to seven times its weight in water. Soil containing biochar is more drought resilient than soil without it. Adsorbed nutrients, tightly sequestered alongside water, get released only as plants need them. Plants must excrete protons (H+) from their roots to disgorge water or positively charged nutrients from the biochar's surface; it's an active process.
Biochar’s surface area (where adsorption happens) can be 500 square meters per gram or more. That is 10% larger than an official NBA basketball court for every gram of biochar. Biochar’s abundant surface area builds protective habitats for soil microbes like fungi and bacteria and many are critical for the health and productivity of the soil itself.
The “carbon sequestration” component of biochar comes into play where “carbon credits” are concerned. There is a financial market for carbon. Not leveraging that market for revenue is foolish. I am climate agnostic. All I care about is that once solid carbon is inside the soil, it will stay there for thousands of years, imparting drought resiliency, fertility collection, nutrient buffering, and release for that time span. I simply want as much solid carbon in the soil because of the undeniably positive effects it has, regardless of any climactic considerations.
Wood Vinegar: More Waste

Another by-product of the gasification process is wood vinegar (Pyroligneous acid). If you have ever seen Liquid Smoke in the grocery store, then you have seen wood vinegar. Principally composed of acetic acid, acetone, and methanol wood vinegar also contains ~200 other organic compounds. It would seem intuitive that condensed, liquefied wood smoke would at least be bad for the health of all living things if not downright carcinogenic. The counter intuition wins the day, however. Wood vinegar has been used by humans for a very long time to promote digestion, bowel, and liver health; combat diarrhea and vomiting; calm peptic ulcers and regulate cholesterol levels; and a host of other benefits.
For centuries humans have annually burned off hundreds of thousands of square miles of pasture, grassland, forest, and every other conceivable terrestrial ecosystem. Why is this done? After every burn, one thing becomes obvious: the almost supernatural growth these ecosystems exhibit after the burn. How? Wood vinegar is a component of this growth. Even in open burns, smoke condenses and infiltrates the soil. That is when wood vinegar shows its quality.
This stuff beefs up not only general plant growth but seed germination as well and possesses many other qualities that are beneficial to plants. It’s a pesticide, fungicide, promotes beneficial soil microorganisms, enhances nutrient uptake, and imparts disease resistance. I am barely touching a long list of attributes here, but you want wood vinegar in your soil (alongside biochar because it adsorbs wood vinegar as well).
The Internal Combustion Engine

Conversion of grazed forage to chemical, then mechanical, and then electrical energy completes the cycle. The ICE (Internal Combustion Engine) converts the gaseous fuel output from the gasifier to mechanical energy, heat, water vapor, and CO2. It’s the mechanical energy of a rotating drive shaft that we want. That rotation drives the electric generator, which is the heartbeat we need to bring this monster to life. Luckily for us, combined internal combustion engine and generator packages are ubiquitous, delivering a defined energy output given a constant fuel input. It’s the simplest part of the system.
The obvious question here is whether the amount of syngas provided by the gasification process will provide enough energy to generate enough electrons to run the entire system or not. While I have no doubt the energy produced will run Forest Walker's main systems the question is really about the electrons left over. Will it be enough to run the Bitcoin mining aspect of the system? Everything is a budget.
CO2 Production For Growth

Plants are lollipops. No matter if it’s a tree or a bush or a shrubbery, the entire thing is mostly sugar in various formats but mostly long chain carbohydrates like lignin and cellulose. Plants need three things to make sugar: CO2, H2O and light. In a forest, where tree densities can be quite high, CO2 availability becomes a limiting growth factor. It’d be in the forest interests to have more available CO2 providing for various sugar formation providing the organism with food and structure.
An odd thing about tree leaves, the openings that allow gasses like the ever searched for CO2 are on the bottom of the leaf (these are called stomata). Not many stomata are topside. This suggests that trees and bushes have evolved to find gasses like CO2 from below, not above and this further suggests CO2 might be in higher concentrations nearer the soil.
The soil life (bacterial, fungi etc.) is constantly producing enormous amounts of CO2 and it would stay in the soil forever (eventually killing the very soil life that produces it) if not for tidal forces. Water is everywhere and whether in pools, lakes, oceans or distributed in “moist” soils water moves towards to the moon. The water in the soil and also in the water tables below the soil rise toward the surface every day. When the water rises, it expels the accumulated gasses in the soil into the atmosphere and it’s mostly CO2. It’s a good bet on how leaves developed high populations of stomata on the underside of leaves. As the water relaxes (the tide goes out) it sucks oxygenated air back into the soil to continue the functions of soil life respiration. The soil “breathes” albeit slowly.
The gasses produced by the Forest Walker’s internal combustion engine consist primarily of CO2 and H2O. Combusting sugars produce the same gasses that are needed to construct the sugars because the universe is funny like that. The Forest Walker is constantly laying down these critical construction elements right where the trees need them: close to the ground to be gobbled up by the trees.
The Branch Drones

During the last ice age, giant mammals populated North America - forests and otherwise. Mastodons, woolly mammoths, rhinos, short-faced bears, steppe bison, caribou, musk ox, giant beavers, camels, gigantic ground-dwelling sloths, glyptodons, and dire wolves were everywhere. Many were ten to fifteen feet tall. As they crashed through forests, they would effectively cleave off dead side-branches of trees, halting the spread of a ground-based fire migrating into the tree crown ("laddering") which is a death knell for a forest.
These animals are all extinct now and forests no longer have any manner of pruning services. But, if we build drones fitted with cutting implements like saws and loppers, optical cameras and AI trained to discern dead branches from living ones, these drones could effectively take over pruning services by identifying, cutting, and dropping to the forest floor, dead branches. The dropped branches simply get collected by the Forest Walker as part of its continual mission.
The drones dock on the back of the Forest Walker to recharge their batteries when low. The whole scene would look like a grazing cow with some flies bothering it. This activity breaks the link between a relatively cool ground based fire and the tree crowns and is a vital element in forest fire control.
The Bitcoin Miner

Mining is one of four monetary incentive models, making this system a possibility for development. The other three are US Dept. of the Interior, township, county, and electrical utility company easement contracts for fuel load management, global carbon credits trading, and data set sales. All the above depends on obvious questions getting answered. I will list some obvious ones, but this is not an engineering document and is not the place for spreadsheets. How much Bitcoin one Forest Walker can mine depends on everything else. What amount of biomass can we process? Will that biomass flow enough Syngas to keep the lights on? Can the chassis support enough mining ASICs and supporting infrastructure? What does that weigh and will it affect field performance? How much power can the AC generator produce?
Other questions that are more philosophical persist. Even if a single Forest Walker can only mine scant amounts of BTC per day, that pales to how much fuel material it can process into biochar. We are talking about millions upon millions of forested acres in need of fuel load management. What can a single Forest Walker do? I am not thinking in singular terms. The Forest Walker must operate as a fleet. What could 50 do? 500?
What is it worth providing a service to the world by managing forest fuel loads? Providing proof of work to the global monetary system? Seeding soil with drought and nutrient resilience by the excretion, over time, of carbon by the ton? What did the last forest fire cost?
The Mesh Network

What could be better than one bitcoin mining, carbon sequestering, forest fire squelching, soil amending behemoth? Thousands of them, but then they would need to be able to talk to each other to coordinate position, data handling, etc. Fitted with a mesh networking device, like goTenna or Meshtastic LoRa equipment enables each Forest Walker to communicate with each other.
Now we have an interconnected fleet of Forest Walkers relaying data to each other and more importantly, aggregating all of that to the last link in the chain for uplink. Well, at least Bitcoin mining data. Since block data is lightweight, transmission of these data via mesh networking in fairly close quartered environs is more than doable. So, how does data transmit to the Bitcoin Network? How do the Forest Walkers get the previous block data necessary to execute on mining?
Back To The Chain

Getting Bitcoin block data to and from the network is the last puzzle piece. The standing presumption here is that wherever a Forest Walker fleet is operating, it is NOT within cell tower range. We further presume that the nearest Walmart Wi-Fi is hours away. Enter the Blockstream Satellite or something like it.
A separate, ground-based drone will have two jobs: To stay as close to the nearest Forest Walker as it can and to provide an antennae for either terrestrial or orbital data uplink. Bitcoin-centric data is transmitted to the "uplink drone" via the mesh networked transmitters and then sent on to the uplink and the whole flow goes in the opposite direction as well; many to one and one to many.
We cannot transmit data to the Blockstream satellite, and it will be up to Blockstream and companies like it to provide uplink capabilities in the future and I don't doubt they will. Starlink you say? What’s stopping that company from filtering out block data? Nothing because it’s Starlink’s system and they could decide to censor these data. It seems we may have a problem sending and receiving Bitcoin data in back country environs.
But, then again, the utility of this system in staunching the fuel load that creates forest fires is extremely useful around forested communities and many have fiber, Wi-Fi and cell towers. These communities could be a welcoming ground zero for first deployments of the Forest Walker system by the home and business owners seeking fire repression. In the best way, Bitcoin subsidizes the safety of the communities.
Sensor Packages
LiDaR

The benefit of having a Forest Walker fleet strolling through the forest is the never ending opportunity for data gathering. A plethora of deployable sensors gathering hyper-accurate data on everything from temperature to topography is yet another revenue generator. Data is valuable and the Forest Walker could generate data sales to various government entities and private concerns.
LiDaR (Light Detection and Ranging) can map topography, perform biomass assessment, comparative soil erosion analysis, etc. It so happens that the Forest Walker’s ability to “see,” to navigate about its surroundings, is LiDaR driven and since it’s already being used, we can get double duty by harvesting that data for later use. By using a laser to send out light pulses and measuring the time it takes for the reflection of those pulses to return, very detailed data sets incrementally build up. Eventually, as enough data about a certain area becomes available, the data becomes useful and valuable.
Forestry concerns, both private and public, often use LiDaR to build 3D models of tree stands to assess the amount of harvest-able lumber in entire sections of forest. Consulting companies offering these services charge anywhere from several hundred to several thousand dollars per square kilometer for such services. A Forest Walker generating such assessments on the fly while performing its other functions is a multi-disciplinary approach to revenue generation.
pH, Soil Moisture, and Cation Exchange Sensing

The Forest Walker is quadrupedal, so there are four contact points to the soil. Why not get a pH data point for every step it takes? We can also gather soil moisture data and cation exchange capacities at unheard of densities because of sampling occurring on the fly during commission of the system’s other duties. No one is going to build a machine to do pH testing of vast tracts of forest soils, but that doesn’t make the data collected from such an endeavor valueless. Since the Forest Walker serves many functions at once, a multitude of data products can add to the return on investment component.
Weather Data

Temperature, humidity, pressure, and even data like evapotranspiration gathered at high densities on broad acre scales have untold value and because the sensors are lightweight and don’t require large power budgets, they come along for the ride at little cost. But, just like the old mantra, “gas, grass, or ass, nobody rides for free”, these sensors provide potential revenue benefits just by them being present.
I’ve touched on just a few data genres here. In fact, the question for universities, governmental bodies, and other institutions becomes, “How much will you pay us to attach your sensor payload to the Forest Walker?”
Noise Suppression

Only you can prevent Metallica filling the surrounds with 120 dB of sound. Easy enough, just turn the car stereo off. But what of a fleet of 50 Forest Walkers operating in the backcountry or near a township? 500? 5000? Each one has a wood chipper, an internal combustion engine, hydraulic pumps, actuators, and more cooling fans than you can shake a stick at. It’s a walking, screaming fire-breathing dragon operating continuously, day and night, twenty-four hours a day, three hundred sixty-five days a year. The sound will negatively affect all living things and that impacts behaviors. Serious engineering consideration and prowess must deliver a silencing blow to the major issue of noise.
It would be foolish to think that a fleet of Forest Walkers could be silent, but if not a major design consideration, then the entire idea is dead on arrival. Townships would not allow them to operate even if they solved the problem of widespread fuel load and neither would governmental entities, and rightly so. Nothing, not man nor beast, would want to be subjected to an eternal, infernal scream even if it were to end within days as the fleet moved further away after consuming what it could. Noise and heat are the only real pollutants of this system; taking noise seriously from the beginning is paramount.
Fire Safety

A “fire-breathing dragon” is not the worst description of the Forest Walker. It eats wood, combusts it at very high temperatures and excretes carbon; and it does so in an extremely flammable environment. Bad mix for one Forest Walker, worse for many. One must take extreme pains to ensure that during normal operation, a Forest Walker could fall over, walk through tinder dry brush, or get pounded into the ground by a meteorite from Krypton and it wouldn’t destroy epic swaths of trees and baby deer. I envision an ultimate test of a prototype to include dowsing it in grain alcohol while it’s wrapped up in toilet paper like a pledge at a fraternity party. If it runs for 72 hours and doesn’t set everything on fire, then maybe outside entities won’t be fearful of something that walks around forests with a constant fire in its belly.
The Wrap

How we think about what can be done with and adjacent to Bitcoin is at least as important as Bitcoin’s economic standing itself. For those who will tell me that this entire idea is without merit, I say, “OK, fine. You can come up with something, too.” What can we plug Bitcoin into that, like a battery, makes something that does not work, work? That’s the lesson I get from this entire exercise. No one was ever going to hire teams of humans to go out and "clean the forest". There's no money in that. The data collection and sales from such an endeavor might provide revenues over the break-even point but investment demands Alpha in this day and age. But, plug Bitcoin into an almost viable system and, voilà! We tip the scales to achieve lift-off.
Let’s face it, we haven’t scratched the surface of Bitcoin’s forcing function on our minds. Not because it’s Bitcoin, but because of what that invention means. The question that pushes me to approach things this way is, “what can we create that one system’s waste is another system’s feedstock?” The Forest Walker system’s only real waste is the conversion of low entropy energy (wood and syngas) into high entropy energy (heat and noise). All other output is beneficial to humanity.
Bitcoin, I believe, is the first product of a new mode of human imagination. An imagination newly forged over the past few millennia of being lied to, stolen from, distracted and otherwise mis-allocated to a black hole of the nonsensical. We are waking up.
What I have presented is not science fiction. Everything I have described here is well within the realm of possibility. The question is one of viability, at least in terms of the detritus of the old world we find ourselves departing from. This system would take a non-trivial amount of time and resources to develop. I think the system would garner extensive long-term contracts from those who have the most to lose from wildfires, the most to gain from hyperaccurate data sets, and, of course, securing the most precious asset in the world. Many may not see it that way, for they seek Alpha and are therefore blind to other possibilities. Others will see only the possibilities; of thinking in a new way, of looking at things differently, and dreaming of what comes next.
-
 @ bf47c19e:c3d2573b
2025-05-11 18:24:44
@ bf47c19e:c3d2573b
2025-05-11 18:24:44Originalni tekst na dvadesetjedan.com.
Autor: Gigi / Prevod na srpski: Plumsky
Postoji sveto carstvo privatnosti za svakog čoveka gde on bira i pravi odluke – carstvo stvoreno na bazičnim pravima i slobode koje zakon, generalno, ne sme narušavati. Džefri Fišer, Arhiepiskop Canterberija (1959)
Pre ne toliko dugo, uobičajen režim interneta je bio neenkriptovan običan tekst (plain text). Svi su mogli špiunirati svakoga i mnogi nisu o tome ni razmišljali. Globalno obelodanjivanje nadzora 2013. je to promenilo i danas se koriste mnogo bezbedniji protokoli i end-to-end enkripcija postaje standard sve više. Iako bitcoin postaje tinejdžer, mi smo – metaforično govoreći – i dalje u dobu običnog teksta narandžastog novčića. Bitcoin je radikalno providljiv protokol sam po sebi, ali postoje značajni načini da korisnik zaštiti svoju privatnost. U ovom članku želimo da istaknemo neke od ovih strategija, prodiskutujemo najbolje prakse, i damo preporuke koje mogu primeniti i bitcoin novajlije i veterani.
Zašto je privatnost bitna
Privatnost je potrebna da bi otvoreno društvo moglo da funkcioniše u digitalnoj eri. Privatnost nije isto što i tajanstvenost. Privatna stvar je nešto što neko ne želi da ceo svet zna, a tajna stvar je nešto što neko ne želi bilo ko da zna. Privatnost je moć da se čovek selektivno otkriva svom okruženju.
Ovim snažnim rečima Erik Hjus je započeo svoj tekst Sajferpankov Manifesto (Cypherpunk's Manifesto) 1993. Razlika između privatnosti i tajanstvenosti je suptilna ali jako važna. Odlučiti se za privatnost ne znači da neko ima tajne koje želi sakriti. Da ovo ilustrujemo shvatite samo da ono što obavljate u svom toaletu ili u spavaćoj sobi nije niti ilegalno niti tajna (u mnogim slučajevima), ali vi svejedno odlučujete da zatvorite vrata i navučete zavese.
Slično tome, koliko para imate i gde ih trošite nije naručito tajna stvar. Ipak, to bi trebalo biti privatan slučaj. Mnogi bi se složili da vaš šef ne treba da zna gde vi trošite vašu platu. Privatnosti je čak zaštićena od strane mnogobrojnih internacionalnih nadležnih organa. Iz Američke Deklaracije Prava i Dužnosti Čoveka (American Declaration of the Rights and Duties of Man) Ujedinjenim Nacijama, napisano je da je privatnost fundamentalno prava gradjana širom sveta.
Niko ne sme biti podvrgnut smetnjama njegovoj privatnosti, porodici, rezidenciji ili komunikacijama, niti napadnuta njegova čast i reputacija. Svi imaju pravo da se štite zakonom protiv takvih smetnja ili napada. Artikal 12, Deklaracija Ljudskih Prava Ujedinjenih Nacija
Bitcoin i privatnost
Iako je bitcoin često opisivan kao anoniman način plaćanja medijima, on u stvari poseduje potpuno suprotne osobine. On je poluanoniman u najboljem slučaju i danas mnogima nije ni malo lako primeniti taktike da bi bili sigurni da njihov poluanonimni identitet na bitcoin mreži ne bude povezan sa legalnim identitetom u stvarnom svetu.
Bitcoin je otvoren sistem. On je javna baza podataka koju svako može da proučava i analizira. Znači, svaka transakcija koja je upisana u tu bazu kroz dokaz rada (proof-of-work) postojaće i biće otkrivena dokle god bitcoin postoji, što znači - zauvek. Ne primenjivati najbolje prakse privatnosti može imati štetne posledice u dalekoj budućnosti.
Privatnost, kao sigurnost, je proces koji je težak, ali nije nemoguć. Alatke nastavljaju da se razvijaju koje čuvaju privatnost kad se koristi bitcoin and srećom mnoge od tih alatki su sve lakše za korišćenje. Nažalost ne postoji panacea u ovom pristupu. Mora se biti svesan svih kompromisa i usavršavati te prakse dok se one menjaju.
Najbolje prakse privatnosti
Kao i sve u bitcoinu, kontrola privatnosti je postepena, korak po korak, procedura. Naučiti i primeniti ove najbolje prakse zahteva strpljivost i odgovornost, tako da ne budite obeshrabreni ako vam se čini da je to sve previše. Svaki korak, koliko god bio mali, je korak u dobrom pravcu.
Koje korake preduzeti da bi uvećali svoju privatnost:
- Budite u vlasništvu sami svojih novčića
- Nikad ne ponavljajte korišćenje istih adresa
- Minimizirajte korišćenje servisa koji zahtevaju identitet (Know your customer - KYC)
- Minimizirajte sve izloženosti trećim licima
- Upravljajte svojim nodom
- Koristite Lightning mrežu za male transakcije
- Nemojte koristiti javne blok pretraživače za svoje transakcije
- Koristite metodu CoinJoin često i rano pri nabavljanju svojih novčića
Budite u vlasništvu sami svojih novčića: Ako ključevi nisu tvoji, onda nije ni bitcoin. Ako neko drugo drži vaš bitcoin za vas, oni znaju sve što se može znati: količinu, istoriju transakcija pa i sve buduće transakcije, itd. Preuzimanje vlasništva bitcoina u svoje ruke je prvi i najvažniji korak.
Nikad ne kroistite istu adresu dvaput: Ponavljanje adresa poništava privatnost pošiljalca i primaoca bitcoina. Ovo se treba izbegavati pod svaku cenu.
Minimizirajte korišćenje servisa koji zahtevaju identitet (KYC): Vezivati svoj legalni identitet za svoje bitcoin adrese je zlo koje se zahteva od strane mnogih državnih nadležnosti. Dok je efektivnost ovih zakona i regulacija disputabilno, posledice njihovog primenjivanja su uglavnom štetne po korisnicima. Ovo je očigledno pošto je česta pojava da se te informacije često izlivaju iz slabo obezbeđenih digitalnih servera. Ako izaberete da koristite KYC servise da bi nabavljali bitcoin, proučite i razumite odnos između vas i tog biznisa. Vi ste poverljivi tom biznisu za sve vaše lične podatke, pa i buduće obezbeđenje tih podataka. Ako i dalje zarađujete kroz fiat novčani sistem, mi preporučujemo da koristite samo bitcoin ekskluzivne servise koji vam dozvoljavaju da autamatski kupujete bitcoin s vremena na vreme. Ako zelite da potpuno da izbegnete KYC, pregledajte https://bitcoinqna.github.io/noKYConly/.
Minimizirajte sve izloženosti trećim licima: Poverljivost trećim licima je bezbednosna rupa (https://nakamotoinstitute.org/trusted-third-parties/). Ako možete biti poverljivi samo sebi, onda bi to tako trebalo da bude.
Upravljajte svojim nodom: Ako nod nije tvoj, onda nisu ni pravila. Upravljanje svojim nodom je suštinska potreba da bi se bitcoin koristio na privatan način. Svaka interakcija sa bitcoin mrežom je posrednjena nodom. Ako vi taj nod ne upravljate, čiji god nod koristite može da vidi sve što vi radite. Ova upustva (https://bitcoiner.guide/node/) su jako korisna da bi započeli proces korišćenja svog noda.
Koristite Lightning mrežu za male transakcije: Pošto Lightning protokol ne koristi glavnu bitcoin mrežu za trasakcije onda je i samim tim povećana privatnost korišćenja bez dodatnog truda. Iako je i dalje rano, oni apsolutno bezobzirni periodi Lightning mreže su verovatno daleko iza nas. Korišćenje Lightning-a za transakcije malih i srednjih veličina će vam pomoći da uvećate privatnost a da smanjite naplate svojih pojedinačnih bitcoin transakcija.
Nemojte koristiti javne blok pretraživače za svoje transakcije: Proveravanje adresa na javnim blok pretraživačima povezuje te adrese sa vašim IP podacima, koji se onda mogu koristiti da se otkrije vaš identitet. Softveri kao Umbrel i myNode vam omogućavaju da lako koristite sami svoj blok pretraživač. Ako morate koristiti javne pretraživače, uradite to uz VPN ili Tor.
Koristite CoinJoin često i rano pri nabavljanju svojih novčića: Pošto je bitcoin večan, primenjivanje saradničkih CoinJoin praksa će vam obezbediti privatnost u budućnosti. Dok su CoinJoin transakcije svakovrsne, softveri koji su laki za korišćenje već sad postoje koji mogu automatizovati ovu vrstu transakcija. Samourai Whirlpool (https://samouraiwallet.com/whirlpool) je odličan izbor za Android korisnike. Joinmarket (https://github.com/joinmarket-webui/jam) se može koristiti na vašem nodu. A servisi postoje koji pri snabdevanju vašeg bitcoina istog trenutka obave CoinJoin tranzakciju automatski.
Zaključak
Svi bi trebalo da se potrude da koriste bitcoin na što privatniji način. Privatnost nije isto što i tajanstvenost. Privatnost je ljudsko pravo i mi svi trebamo da branimo i primenljujemo to pravo. Teško je izbrisati postojeće informacije sa interneta; a izbrisati ih sa bitcoin baze podataka je nemoguće. Iako su daleko od savršenih, alatke postoje danas koje vam omogućavaju da najbolje prakse privatnosti i vi sami primenite. Mi smo vam naglasili neke od njih i - kroz poboljšanje u bitcoin protokolu kroz Taproot i Schnorr - one će postajati sve usavršenije.
Bitcoin postupci se ne mogu lako opisati korišćenjem tradicionalnim konceptima. Pitanja kao što su "Ko je vlasnik ovog novca?" ili "Odakle taj novac potiče?" postaju sve teža da se odgovore a u nekim okolnostima postaju potpuno beznačajna.
Satoši je dizajnirao bitcoin misleći na privatnost. Na nivou protokola svaka bitcoin transakcija je proces "topljenja" koji za sobom samo ostavlja heuristične mrvice hleba. Protokolu nije bitno odakle se pojavio bilo koji bitcoin ili satoši. Niti je njega briga ko je legalan identitet vlasnika. Protokolu je samo važno da li su digitalni potpisi validni. Dokle god je govor slobodan, potpisivanje poruka - privatno ili ne - ne sme biti kriminalan postupak.
Dodatni Resursi
This Month in Bitcoin Privacy | Janine
Hodl Privacy FAQ | 6102
Digital Privacy | 6102
UseWhirlpool.com | Bitcoin Q+A
Bitcoin Privacy Guide | Bitcoin Q+A
Ovaj članak napisan je u saradnji sa Matt Odellom, nezavisnim bitcoin istraživačem. Nađite njegove preporuke za privatnost na werunbtc.com
-
 @ bf47c19e:c3d2573b
2025-05-11 18:24:28
@ bf47c19e:c3d2573b
2025-05-11 18:24:28Originalni tekst na dvadesetjedan.com.
Autor: Matt Corallo / Prevod na hrvatski: Davor
Bitcoineri, od programera Bitcoin Core-a preko dugogodišnjih entuzijasta Bitcoina do nedavnih pronalazača /r/Bitcoina, vole razgovarati o tome kako je decentralizacija Bitcoina njegova ultimativna značajka. Doduše, rijetko vidite da netko objašnjava zašto je decentralizacija važna. Zasigurno je to zanimljiva značajka iz perspektive računalne znanosti, no zašto bi potrošači, tvrtke ili investitori marili za to? Ova objava je pokušaj da se napiše zašto je decentralizacija temelj vrijednosti Bitcoina i što je još važnije, postavi buduće objave u kojima se govori o tome kada ona to nije.
Kada Bitcoineri govore o decentralizaciji Bitcoina, prva stvar koja se pojavljuje je često spominjani nedostatak inherentnog povjerenja u treću stranu. Dok je dobro postavljeno povjerenje preduvjet za učinkovit rad mnogih sustava, jednom kada se takvo povjerenje izgubi, sustavi mogu postati nevjerojatno krhki. Uzmimo, za primjer, povjerenje u američke banke prije uspostave FDIC-a (Federal Deposit Insurance Corporation). Dok je pristup bankovnim uslugama omogućio više pogodnosti i mnogim tvrtkama učinkovitije poslovanje, poznato je da su banke propadale, pritom upropaštavajući sa sobom sva sredstva klijenata. Dok je predstavljanje FDIC-a i sličnih programa decentraliziralo povjerenje u financijske institucije s jedne strane na dvije, transakcije u velikom dijelu svijeta ne nude takvu zaštitu. Čak i uz takve programe, pojedinci nisu univerzalno zaštićeni od gubitka preko granica i preko određene vrijednosti.
U novije vrijeme, propisi koji dopuštaju pojedinim državnim dužnosnicima jednostrano oduzimanje imovine postali su uobičajeni. Naročito u SAD-u, sada zloglasna “Operacija Choke Point” i programi oduzimanja civilne imovine, omogućili su službenicima za provođenje zakona i privatnim institucijama da zapljenjuju financijsku imovinu i uskraćuju financijske usluge uz malo ili nimalo nadzora. Uklanjanje provjerenih skrbnika i stvaranje sustava s likvidnom imovinom, koja se ne može zaplijeniti, ima potencijal pružiti pouzdanije financijske usluge mnogima koji inače ne bi mogli djelovati učinkovito ili uopće ne bi mogli djelovati. Ova mogućnost da se Bitcoin ne može zaplijeniti, omogućena je samo zbog nedostatka za centraliziranim povjerenjem. Centralizirani sustavi elektroničke gotovine i financijski sustavi su pokušali pružiti takvu pouzdanost, propisi i poslovna stvarnost su to gotovo univerzalno spriječili.
Svojstvo koje je jednako važno za sposobnost Bitcoina da pruža financijske usluge zviždačima, stranim disidentima i porno zvijezdama je njegov otpor cenzuri transakcija. Sposobnost trećih strana da zaplijene imovinu rezultira izravnim i čistim novčanim gubitkom, zamrzavanje imovine može imati sličan učinak. Kada pojedinac ili organizacija više nisu u mogućnosti obavljati transakcije za plaćanje roba i usluga, njihova financijska imovina brzo gubi vrijednost. Iako Bitcoin ima vrlo dobru priču o nemogućnosti zapljene (svaka strana u sustavu nameće nemogućnost bilo koga da potroši Bitcoin bez dodanog privatnog ključa), njegova priča o otporu cenzuri je malo utančanija.
U svijetu u kojem nijedan rudar Bitcoina nema više od 1% ukupne hash snage (ili nešto drugo što je jednako decentralizirano), trebalo bi biti lako pronaći rudara koji je ili anoniman i prihvaća sve transakcije ili je u nadležnosti koja ne pokušava cenzurirati vaše transakcije. Naravno, ovo nije svijet kakav danas imamo, a cenzura transakcija jedan je od većih razloga da se ozbiljno zabrinemo centralizacijom rudarenja (za pune čvorove). Ipak, mogućnost pojedinca da kupi hash snagu (u obliku lako dostupnog starog hardvera ili u obliku njegovog iznajmljivanja) za rudarenje svoje inače cenzurirane transakcije, opcija je sve dok je pravilo najdužeg lanca na snazi kod svih rudara. Iako je znatno skuplji nego što bi bio u istinski decentraliziranom Bitcoinu, to omogućuje Bitcoinu da zadrži neka od svojih anti-cenzuriranih svojstava.
Ako ste već dovoljno dugo u priči oko Bitcoina, možda ćete prepoznati gornja svojstva kao kritična za zamjenjivost. Zamjenjivost, kao ključno svojstvo svakog monetarnog instrumenta, odnosi se na ideju da vrijednost jedne jedinice treba biti ekvivalentna svakoj drugoj jedinici. Bez mogućnosti odmrzavanja/otpora cenzuri i nemogućnosti zapljene, Bitcoin (i svaki drugi monetarni sustav) počinje gubiti zamjenjivost. Trgovci i platni procesori više ne mogu razumno prihvaćati Bitcoin bez provjere niza crnih lista i mnogo truda kako bi bili sigurni da će moći potrošiti Bitcoin koji prihvaćaju. Ako povjerenje u zamjenjivost Bitcoina deformira, njegova bi korist mogla biti značajno deformirana.
Još jedno svojstvo koje proizlazi iz decentralizacije Bitcoina, je njegov otvoreni pristup. Ulagači iz Silicijske doline često ga nazivaju jednim od najzanimljivijih svojstava Bitcoina, a mnogi ga vole nazivati "bez dopuštenja". Sposobnost bilo koga, bilo gdje u svijetu, sa internetskom vezom, da prihvaća Bitcoin za robu i usluge i koristi Bitcoin za kupnju roba i usluga je vrlo uzbudljiva. Opet, ovo svojstvo ovisi o decentralizaciji Bitcoina. Iako postoje mnogi centralizirani pružatelji financijskih usluga, gdje mnogi od njih promoviraju svoju dostupnost bilo kome, sama njihova prisutnost kao centraliziranog tijela koje može proizvoljno uskratiti uslugu, čini ih podložnim budućim promjenama politike iz bilo kojeg razloga. PayPal je, na primjer, utemeljen na idealima univerzalnog pristupa elektroničkoj gotovini. Međutim, zbog svoje pozicije središnje vlasti, brzo je promijenio svoje politike, kako bi udovoljio pritiscima regulatora i politikama postojećeg financijskog sustava na koji se oslanjao. Ovih dana, PayPal je nadaleko poznat po zamrzavanju računa i oduzimanju imovine uz malo ili nimalo upozorenja. U osnovi, oslanjanje na centralizirane strane za usluge nije kompatibilno s univerzalnim otvorenim pristupom u financijskom svijetu.
Primijetit ćete da se sve gore navedene kritične značajke, one koje Bitcoin čine tako uzbudljivim za sve nas, centralizirani sistemi već neko vrijeme mogu implementirati. Zapravo to se radilo i prije, u učinkovitijim sustavima od Bitcoina. Naravno, nikada nisu potrajali, gubeći kritična svojstva nakon podešavanja kako bi se popravila ova ili ona stvar, implementirajući regulatorne sustave cenzure izravno u osnovne slojeve, ograničavajući pristup rastu dobiti i potpuno gašenje. Stvarno, decentralizacija u Bitcoinu sama po sebi nije značajka, već je umjesto toga jedini način za koji znamo da održimo značajke koje želimo u sustavima kojima upravljaju ljudi.
-
 @ e3ba5e1a:5e433365
2025-01-13 16:47:27
@ e3ba5e1a:5e433365
2025-01-13 16:47:27My blog posts and reading material have both been on a decidedly economics-heavy slant recently. The topic today, incentives, squarely falls into the category of economics. However, when I say economics, I’m not talking about “analyzing supply and demand curves.” I’m talking about the true basis of economics: understanding how human beings make decisions in a world of scarcity.
A fair definition of incentive is “a reward or punishment that motivates behavior to achieve a desired outcome.” When most people think about economic incentives, they’re thinking of money. If I offer my son $5 if he washes the dishes, I’m incentivizing certain behavior. We can’t guarantee that he’ll do what I want him to do, but we can agree that the incentive structure itself will guide and ultimately determine what outcome will occur.
The great thing about monetary incentives is how easy they are to talk about and compare. “Would I rather make $5 washing the dishes or $10 cleaning the gutters?” But much of the world is incentivized in non-monetary ways too. For example, using the “punishment” half of the definition above, I might threaten my son with losing Nintendo Switch access if he doesn’t wash the dishes. No money is involved, but I’m still incentivizing behavior.
And there are plenty of incentives beyond our direct control! My son is also incentivized to not wash dishes because it’s boring, or because he has some friends over that he wants to hang out with, or dozens of other things. Ultimately, the conflicting array of different incentive structures placed on him will ultimately determine what actions he chooses to take.
Why incentives matter
A phrase I see often in discussions—whether they are political, parenting, economic, or business—is “if they could just do…” Each time I see that phrase, I cringe a bit internally. Usually, the underlying assumption of the statement is “if people would behave contrary to their incentivized behavior then things would be better.” For example:
- If my kids would just go to bed when I tell them, they wouldn’t be so cranky in the morning.
- If people would just use the recycling bin, we wouldn’t have such a landfill problem.
- If people would just stop being lazy, our team would deliver our project on time.
In all these cases, the speakers are seemingly flummoxed as to why the people in question don’t behave more rationally. The problem is: each group is behaving perfectly rationally.
- The kids have a high time preference, and care more about the joy of staying up now than the crankiness in the morning. Plus, they don’t really suffer the consequences of morning crankiness, their parents do.
- No individual suffers much from their individual contribution to a landfill. If they stopped growing the size of the landfill, it would make an insignificant difference versus the amount of effort they need to engage in to properly recycle.
- If a team doesn’t properly account for the productivity of individuals on a project, each individual receives less harm from their own inaction. Sure, the project may be delayed, company revenue may be down, and they may even risk losing their job when the company goes out of business. But their laziness individually won’t determine the entirety of that outcome. By contrast, they greatly benefit from being lazy by getting to relax at work, go on social media, read a book, or do whatever else they do when they’re supposed to be working.

My point here is that, as long as you ignore the reality of how incentives drive human behavior, you’ll fail at getting the outcomes you want.
If everything I wrote up until now made perfect sense, you understand the premise of this blog post. The rest of it will focus on a bunch of real-world examples to hammer home the point, and demonstrate how versatile this mental model is.
Running a company
Let’s say I run my own company, with myself as the only employee. My personal revenue will be 100% determined by my own actions. If I decide to take Tuesday afternoon off and go fishing, I’ve chosen to lose that afternoon’s revenue. Implicitly, I’ve decided that the enjoyment I get from an afternoon of fishing is greater than the potential revenue. You may think I’m being lazy, but it’s my decision to make. In this situation, the incentive–money–is perfectly aligned with my actions.
Compare this to a typical company/employee relationship. I might have a bank of Paid Time Off (PTO) days, in which case once again my incentives are relatively aligned. I know that I can take off 15 days throughout the year, and I’ve chosen to use half a day for the fishing trip. All is still good.
What about unlimited time off? Suddenly incentives are starting to misalign. I don’t directly pay a price for not showing up to work on Tuesday. Or Wednesday as well, for that matter. I might ultimately be fired for not doing my job, but that will take longer to work its way through the system than simply not making any money for the day taken off.
Compensation overall falls into this misaligned incentive structure. Let’s forget about taking time off. Instead, I work full time on a software project I’m assigned. But instead of using the normal toolchain we’re all used to at work, I play around with a new programming language. I get the fun and joy of playing with new technology, and potentially get to pad my resume a bit when I’m ready to look for a new job. But my current company gets slower results, less productivity, and is forced to subsidize my extracurricular learning.
When a CEO has a bonus structure based on profitability, he’ll do everything he can to make the company profitable. This might include things that actually benefit the company, like improving product quality, reducing internal red tape, or finding cheaper vendors. But it might also include destructive practices, like slashing the R\&D budget to show massive profits this year, in exchange for a catastrophe next year when the next version of the product fails to ship.

Or my favorite example. My parents owned a business when I was growing up. They had a back office where they ran operations like accounting. All of the furniture was old couches from our house. After all, any money they spent on furniture came right out of their paychecks! But in a large corporate environment, each department is generally given a budget for office furniture, a budget which doesn’t roll over year-to-year. The result? Executives make sure to spend the entire budget each year, often buying furniture far more expensive than they would choose if it was their own money.
There are plenty of details you can quibble with above. It’s in a company’s best interest to give people downtime so that they can come back recharged. Having good ergonomic furniture can in fact increase productivity in excess of the money spent on it. But overall, the picture is pretty clear: in large corporate structures, you’re guaranteed to have mismatches between the company’s goals and the incentive structure placed on individuals.
Using our model from above, we can lament how lazy, greedy, and unethical the employees are for doing what they’re incentivized to do instead of what’s right. But that’s simply ignoring the reality of human nature.
Moral hazard
Moral hazard is a situation where one party is incentivized to take on more risk because another party will bear the consequences. Suppose I tell my son when he turns 21 (or whatever legal gambling age is) that I’ll cover all his losses for a day at the casino, but he gets to keep all the winnings.
What do you think he’s going to do? The most logical course of action is to place the largest possible bets for as long as possible, asking me to cover each time he loses, and taking money off the table and into his bank account each time he wins.

But let’s look at a slightly more nuanced example. I go to a bathroom in the mall. As I’m leaving, I wash my hands. It will take me an extra 1 second to turn off the water when I’m done washing. That’s a trivial price to pay. If I don’t turn off the water, the mall will have to pay for many liters of wasted water, benefiting no one. But I won’t suffer any consequences at all.
This is also a moral hazard, but most people will still turn off the water. Why? Usually due to some combination of other reasons such as:
- We’re so habituated to turning off the water that we don’t even consider not turning it off. Put differently, the mental effort needed to not turn off the water is more expensive than the 1 second of time to turn it off.
- Many of us have been brought up with a deep guilt about wasting resources like water. We have an internal incentive structure that makes the 1 second to turn off the water much less costly than the mental anguish of the waste we created.
- We’re afraid we’ll be caught by someone else and face some kind of social repercussions. (Or maybe more than social. Are you sure there isn’t a law against leaving the water tap on?)
Even with all that in place, you may notice that many public bathrooms use automatic water dispensers. Sure, there’s a sanitation reason for that, but it’s also to avoid this moral hazard.
A common denominator in both of these is that the person taking the action that causes the liability (either the gambling or leaving the water on) is not the person who bears the responsibility for that liability (the father or the mall owner). Generally speaking, the closer together the person making the decision and the person incurring the liability are, the smaller the moral hazard.
It’s easy to demonstrate that by extending the casino example a bit. I said it was the father who was covering the losses of the gambler. Many children (though not all) would want to avoid totally bankrupting their parents, or at least financially hurting them. Instead, imagine that someone from the IRS shows up at your door, hands you a credit card, and tells you you can use it at a casino all day, taking home all the chips you want. The money is coming from the government. How many people would put any restriction on how much they spend?
And since we’re talking about the government already…
Government moral hazards
As I was preparing to write this blog post, the California wildfires hit. The discussions around those wildfires gave a huge number of examples of moral hazards. I decided to cherry-pick a few for this post.
The first and most obvious one: California is asking for disaster relief funds from the federal government. That sounds wonderful. These fires were a natural disaster, so why shouldn’t the federal government pitch in and help take care of people?
The problem is, once again, a moral hazard. In the case of the wildfires, California and Los Angeles both had ample actions they could have taken to mitigate the destruction of this fire: better forest management, larger fire department, keeping the water reservoirs filled, and probably much more that hasn’t come to light yet.
If the federal government bails out California, it will be a clear message for the future: your mistakes will be fixed by others. You know what kind of behavior that incentivizes? More risky behavior! Why spend state funds on forest management and extra firefighters—activities that don’t win politicians a lot of votes in general—when you could instead spend it on a football stadium, higher unemployment payments, or anything else, and then let the feds cover the cost of screw-ups.
You may notice that this is virtually identical to the 2008 “too big to fail” bail-outs. Wall Street took insanely risky behavior, reaped huge profits for years, and when they eventually got caught with their pants down, the rest of us bailed them out. “Privatizing profits, socializing losses.”

And here’s the absolute best part of this: I can’t even truly blame either California or Wall Street. (I mean, I do blame them, I think their behavior is reprehensible, but you’ll see what I mean.) In a world where the rules of the game implicitly include the bail-out mentality, you would be harming your citizens/shareholders/investors if you didn’t engage in that risky behavior. Since everyone is on the hook for those socialized losses, your best bet is to maximize those privatized profits.
There’s a lot more to government and moral hazard, but I think these two cases demonstrate the crux pretty solidly. But let’s leave moral hazard behind for a bit and get to general incentivization discussions.
Non-monetary competition
At least 50% of the economics knowledge I have comes from the very first econ course I took in college. That professor was amazing, and had some very colorful stories. I can’t vouch for the veracity of the two I’m about to share, but they definitely drive the point home.
In the 1970s, the US had an oil shortage. To “fix” this problem, they instituted price caps on gasoline, which of course resulted in insufficient gasoline. To “fix” this problem, they instituted policies where, depending on your license plate number, you could only fill up gas on certain days of the week. (Irrelevant detail for our point here, but this just resulted in people filling up their tanks more often, no reduction in gas usage.)
Anyway, my professor’s wife had a friend. My professor described in great detail how attractive this woman was. I’ll skip those details here since this is a PG-rated blog. In any event, she never had any trouble filling up her gas tank any day of the week. She would drive up, be told she couldn’t fill up gas today, bat her eyes at the attendant, explain how helpless she was, and was always allowed to fill up gas.
This is a demonstration of non-monetary compensation. Most of the time in a free market, capitalist economy, people are compensated through money. When price caps come into play, there’s a limit to how much monetary compensation someone can receive. And in that case, people find other ways of competing. Like this woman’s case: through using flirtatious behavior to compensate the gas station workers to let her cheat the rules.
The other example was much more insidious. Santa Monica had a problem: it was predominantly wealthy and white. They wanted to fix this problem, and decided to put in place rent controls. After some time, they discovered that Santa Monica had become wealthier and whiter, the exact opposite of their desired outcome. Why would that happen?
Someone investigated, and ended up interviewing a landlady that demonstrated the reason. She was an older white woman, and admittedly racist. Prior to the rent controls, she would list her apartments in the newspaper, and would be legally obligated to rent to anyone who could afford it. Once rent controls were in place, she took a different tact. She knew that she would only get a certain amount for the apartment, and that the demand for apartments was higher than the supply. That meant she could be picky.
She ended up finding tenants through friends-of-friends. Since it wasn’t an official advertisement, she wasn’t legally required to rent it out if someone could afford to pay. Instead, she got to interview people individually and then make them an offer. Normally, that would have resulted in receiving a lower rental price, but not under rent controls.
So who did she choose? A young, unmarried, wealthy, white woman. It made perfect sense. Women were less intimidating and more likely to maintain the apartment better. Wealthy people, she determined, would be better tenants. (I have no idea if this is true in practice or not, I’m not a landlord myself.) Unmarried, because no kids running around meant less damage to the property. And, of course, white. Because she was racist, and her incentive structure made her prefer whites.
You can deride her for being racist, I won’t disagree with you. But it’s simply the reality. Under the non-rent-control scenario, her profit motive for money outweighed her racism motive. But under rent control, the monetary competition was removed, and she was free to play into her racist tendencies without facing any negative consequences.
Bureaucracy
These were the two examples I remember for that course. But non-monetary compensation pops up in many more places. One highly pertinent example is bureaucracies. Imagine you have a government office, or a large corporation’s acquisition department, or the team that apportions grants at a university. In all these cases, you have a group of people making decisions about handing out money that has no monetary impact on them. If they give to the best qualified recipients, they receive no raises. If they spend the money recklessly on frivolous projects, they face no consequences.
Under such an incentivization scheme, there’s little to encourage the bureaucrats to make intelligent funding decisions. Instead, they’ll be incentivized to spend the money where they recognize non-monetary benefits. This is why it’s so common to hear about expensive meals, gift bags at conferences, and even more inappropriate ways of trying to curry favor with those that hold the purse strings.
Compare that ever so briefly with the purchases made by a small mom-and-pop store like my parents owned. Could my dad take a bribe to buy from a vendor who’s ripping him off? Absolutely he could! But he’d lose more on the deal than he’d make on the bribe, since he’s directly incentivized by the deal itself. It would make much more sense for him to go with the better vendor, save $5,000 on the deal, and then treat himself to a lavish $400 meal to celebrate.
Government incentivized behavior
This post is getting longer in the tooth than I’d intended, so I’ll finish off with this section and make it a bit briefer. Beyond all the methods mentioned above, government has another mechanism for modifying behavior: through directly changing incentives via legislation, regulation, and monetary policy. Let’s see some examples:
- Artificial modification of interest rates encourages people to take on more debt than they would in a free capital market, leading to malinvestment and a consumer debt crisis, and causing the boom-bust cycle we all painfully experience.
- Going along with that, giving tax breaks on interest payments further artificially incentivizes people to take on debt that they wouldn’t otherwise.
- During COVID-19, at some points unemployment benefits were greater than minimum wage, incentivizing people to rather stay home and not work than get a job, leading to reduced overall productivity in the economy and more printed dollars for benefits. In other words, it was a perfect recipe for inflation.
- The tax code gives deductions to “help” people. That might be true, but the real impact is incentivizing people to make decisions they wouldn’t have otherwise. For example, giving out tax deductions on children encourages having more kids. Tax deductions on childcare and preschools incentivizes dual-income households. Whether or not you like the outcomes, it’s clear that it’s government that’s encouraging these outcomes to happen.
- Tax incentives cause people to engage in behavior they wouldn’t otherwise (daycare+working mother, for example).
- Inflation means that the value of your money goes down over time, which encourages people to spend more today, when their money has a larger impact. (Milton Friedman described this as high living.)
Conclusion
The idea here is simple, and fully encapsulated in the title: incentives determine outcomes. If you want to know how to get a certain outcome from others, incentivize them to want that to happen. If you want to understand why people act in seemingly irrational ways, check their incentives. If you’re confused why leaders (and especially politicians) seem to engage in destructive behavior, check their incentives.
We can bemoan these realities all we want, but they are realities. While there are some people who have a solid internal moral and ethical code, and that internal code incentivizes them to behave against their externally-incentivized interests, those people are rare. And frankly, those people are self-defeating. People should take advantage of the incentives around them. Because if they don’t, someone else will.
(If you want a literary example of that last comment, see the horse in Animal Farm.)
How do we improve the world under these conditions? Make sure the incentives align well with the overall goals of society. To me, it’s a simple formula:
- Focus on free trade, value for value, as the basis of a society. In that system, people are always incentivized to provide value to other people.
- Reduce the size of bureaucracies and large groups of all kinds. The larger an organization becomes, the farther the consequences of decisions are from those who make them.
- And since the nature of human beings will be to try and create areas where they can control the incentive systems to their own benefits, make that as difficult as possible. That comes in the form of strict limits on government power, for example.
And even if you don’t want to buy in to this conclusion, I hope the rest of the content was educational, and maybe a bit entertaining!
-
 @ 26d4b5b2:96393e73
2025-05-11 22:24:38
@ 26d4b5b2:96393e73
2025-05-11 22:24:38https://app.doh.money http://localhost:3000 https://dohmoney-cyxe-cyxeio-cyxecyxeios-projects.vercel.app GET POST OPTIONS PUT DELETE Content-Type Ocp-Apim-Subscription-Key Authorization Accept X-Requested-With X-Verified-By Content-Length Request-Context Date @(context.Request.Headers.GetValueOrDefault("Ocp-Apim-Subscription-Key", "50922ff015c14a84a092b4764dc6dddf")) @(context.Request.Headers.GetValueOrDefault("Origin", "https://app.doh.money")) @(context.Request.Headers.GetValueOrDefault("Origin", "http://localhost:3000")) GET, POST, OPTIONS, PUT, DELETE Content-Type, Ocp-Apim-Subscription-Key, Authorization, Accept, X-Requested-With,X-Verified-By Content-Length, Request-Context, Date @(context.Request.Headers.GetValueOrDefault("Origin", "https://app.doh.money")) @(context.Request.Headers.GetValueOrDefault("Origin", "http://localhost:3000")) GET, POST, OPTIONS, PUT, DELETE Content-Type, Ocp-Apim-Subscription-Key, Authorization, Accept, X-Requested-With, X-Verified-By Content-Length, Request-Context, Date -
 @ 3f770d65:7a745b24
2025-01-12 21:03:36
@ 3f770d65:7a745b24
2025-01-12 21:03:36I’ve been using Notedeck for several months, starting with its extremely early and experimental alpha versions, all the way to its current, more stable alpha releases. The journey has been fascinating, as I’ve had the privilege of watching it evolve from a concept into a functional and promising tool.
In its earliest stages, Notedeck was raw—offering glimpses of its potential but still far from practical for daily use. Even then, the vision behind it was clear: a platform designed to redefine how we interact with Nostr by offering flexibility and power for all users.
I'm very bullish on Notedeck. Why? Because Will Casarin is making it! Duh! 😂
Seriously though, if we’re reimagining the web and rebuilding portions of the Internet, it’s important to recognize the potential of Notedeck. If Nostr is reimagining the web, then Notedeck is reimagining the Nostr client.
Notedeck isn’t just another Nostr app—it’s more a Nostr browser that functions more like an operating system with micro-apps. How cool is that?
Much like how Google's Chrome evolved from being a web browser with a task manager into ChromeOS, a full blown operating system, Notedeck aims to transform how we interact with the Nostr. It goes beyond individual apps, offering a foundation for a fully integrated ecosystem built around Nostr.
As a Nostr evangelist, I love to scream INTEROPERABILITY and tout every application's integrations. Well, Notedeck has the potential to be one of the best platforms to showcase these integrations in entirely new and exciting ways.
Do you want an Olas feed of images? Add the media column.
Do you want a feed of live video events? Add the zap.stream column.
Do you want Nostr Nests or audio chats? Add that column to your Notedeck.
Git? Email? Books? Chat and DMs? It's all possible.
Not everyone wants a super app though, and that’s okay. As with most things in the Nostr ecosystem, flexibility is key. Notedeck gives users the freedom to choose how they engage with it—whether it’s simply following hashtags or managing straightforward feeds. You'll be able to tailor Notedeck to fit your needs, using it as extensively or minimally as you prefer.
Notedeck is designed with a local-first approach, utilizing Nostr content stored directly on your device via the local nostrdb. This will enable a plethora of advanced tools such as search and filtering, the creation of custom feeds, and the ability to develop personalized algorithms across multiple Notedeck micro-applications—all with unparalleled flexibility.
Notedeck also supports multicast. Let's geek out for a second. Multicast is a method of communication where data is sent from one source to multiple destinations simultaneously, but only to devices that wish to receive the data. Unlike broadcast, which sends data to all devices on a network, multicast targets specific receivers, reducing network traffic. This is commonly used for efficient data distribution in scenarios like streaming, conferencing, or large-scale data synchronization between devices.
In a local first world where each device holds local copies of your nostr nodes, and each device transparently syncs with each other on the local network, each node becomes a backup. Your data becomes antifragile automatically. When a node goes down it can resync and recover from other nodes. Even if not all nodes have a complete collection, negentropy can pull down only what is needed from each device. All this can be done without internet.
-Will Casarin
In the context of Notedeck, multicast would allow multiple devices to sync their Nostr nodes with each other over a local network without needing an internet connection. Wild.
Notedeck aims to offer full customization too, including the ability to design and share custom skins, much like Winamp. Users will also be able to create personalized columns and, in the future, share their setups with others. This opens the door for power users to craft tailored Nostr experiences, leveraging their expertise in the protocol and applications. By sharing these configurations as "Starter Decks," they can simplify onboarding and showcase the best of Nostr’s ecosystem.
Nostr’s “Other Stuff” can often be difficult to discover, use, or understand. Many users doesn't understand or know how to use web browser extensions to login to applications. Let's not even get started with nsecbunkers. Notedeck will address this challenge by providing a native experience that brings these lesser-known applications, tools, and content into a user-friendly and accessible interface, making exploration seamless. However, that doesn't mean Notedeck should disregard power users that want to use nsecbunkers though - hint hint.
For anyone interested in watching Nostr be developed live, right before your very eyes, Notedeck’s progress serves as a reminder of what’s possible when innovation meets dedication. The current alpha is already demonstrating its ability to handle complex use cases, and I’m excited to see how it continues to grow as it moves toward a full release later this year.
-
 @ 26d4b5b2:96393e73
2025-05-11 21:44:26
@ 26d4b5b2:96393e73
2025-05-11 21:44:26@(context.Request.Headers.GetValueOrDefault("Origin", "")) GET, POST, OPTIONS, PUT, DELETE Content-Type, Authorization, Accept, X-Requested-With, X-Verified-By, Ocp-Apim-Subscription-Key 86400 Access denied: invalid origin {{dohcloud-key}} @(context.Request.Headers.GetValueOrDefault("Origin", "")) GET, POST, OPTIONS, PUT, DELETE Content-Type, Authorization, Accept, X-Requested-With, X-Verified-By, Ocp-Apim-Subscription-Key @(context.Request.Headers.GetValueOrDefault("Origin", "*")) -
 @ 0d97beae:c5274a14
2025-01-11 16:52:08
@ 0d97beae:c5274a14
2025-01-11 16:52:08This article hopes to complement the article by Lyn Alden on YouTube: https://www.youtube.com/watch?v=jk_HWmmwiAs
The reason why we have broken money
Before the invention of key technologies such as the printing press and electronic communications, even such as those as early as morse code transmitters, gold had won the competition for best medium of money around the world.
In fact, it was not just gold by itself that became money, rulers and world leaders developed coins in order to help the economy grow. Gold nuggets were not as easy to transact with as coins with specific imprints and denominated sizes.
However, these modern technologies created massive efficiencies that allowed us to communicate and perform services more efficiently and much faster, yet the medium of money could not benefit from these advancements. Gold was heavy, slow and expensive to move globally, even though requesting and performing services globally did not have this limitation anymore.
Banks took initiative and created derivatives of gold: paper and electronic money; these new currencies allowed the economy to continue to grow and evolve, but it was not without its dark side. Today, no currency is denominated in gold at all, money is backed by nothing and its inherent value, the paper it is printed on, is worthless too.
Banks and governments eventually transitioned from a money derivative to a system of debt that could be co-opted and controlled for political and personal reasons. Our money today is broken and is the cause of more expensive, poorer quality goods in the economy, a larger and ever growing wealth gap, and many of the follow-on problems that have come with it.
Bitcoin overcomes the "transfer of hard money" problem
Just like gold coins were created by man, Bitcoin too is a technology created by man. Bitcoin, however is a much more profound invention, possibly more of a discovery than an invention in fact. Bitcoin has proven to be unbreakable, incorruptible and has upheld its ability to keep its units scarce, inalienable and counterfeit proof through the nature of its own design.
Since Bitcoin is a digital technology, it can be transferred across international borders almost as quickly as information itself. It therefore severely reduces the need for a derivative to be used to represent money to facilitate digital trade. This means that as the currency we use today continues to fare poorly for many people, bitcoin will continue to stand out as hard money, that just so happens to work as well, functionally, along side it.
Bitcoin will also always be available to anyone who wishes to earn it directly; even China is unable to restrict its citizens from accessing it. The dollar has traditionally become the currency for people who discover that their local currency is unsustainable. Even when the dollar has become illegal to use, it is simply used privately and unofficially. However, because bitcoin does not require you to trade it at a bank in order to use it across borders and across the web, Bitcoin will continue to be a viable escape hatch until we one day hit some critical mass where the world has simply adopted Bitcoin globally and everyone else must adopt it to survive.
Bitcoin has not yet proven that it can support the world at scale. However it can only be tested through real adoption, and just as gold coins were developed to help gold scale, tools will be developed to help overcome problems as they arise; ideally without the need for another derivative, but if necessary, hopefully with one that is more neutral and less corruptible than the derivatives used to represent gold.
Bitcoin blurs the line between commodity and technology
Bitcoin is a technology, it is a tool that requires human involvement to function, however it surprisingly does not allow for any concentration of power. Anyone can help to facilitate Bitcoin's operations, but no one can take control of its behaviour, its reach, or its prioritisation, as it operates autonomously based on a pre-determined, neutral set of rules.
At the same time, its built-in incentive mechanism ensures that people do not have to operate bitcoin out of the good of their heart. Even though the system cannot be co-opted holistically, It will not stop operating while there are people motivated to trade their time and resources to keep it running and earn from others' transaction fees. Although it requires humans to operate it, it remains both neutral and sustainable.
Never before have we developed or discovered a technology that could not be co-opted and used by one person or faction against another. Due to this nature, Bitcoin's units are often described as a commodity; they cannot be usurped or virtually cloned, and they cannot be affected by political biases.
The dangers of derivatives
A derivative is something created, designed or developed to represent another thing in order to solve a particular complication or problem. For example, paper and electronic money was once a derivative of gold.
In the case of Bitcoin, if you cannot link your units of bitcoin to an "address" that you personally hold a cryptographically secure key to, then you very likely have a derivative of bitcoin, not bitcoin itself. If you buy bitcoin on an online exchange and do not withdraw the bitcoin to a wallet that you control, then you legally own an electronic derivative of bitcoin.
Bitcoin is a new technology. It will have a learning curve and it will take time for humanity to learn how to comprehend, authenticate and take control of bitcoin collectively. Having said that, many people all over the world are already using and relying on Bitcoin natively. For many, it will require for people to find the need or a desire for a neutral money like bitcoin, and to have been burned by derivatives of it, before they start to understand the difference between the two. Eventually, it will become an essential part of what we regard as common sense.
Learn for yourself
If you wish to learn more about how to handle bitcoin and avoid derivatives, you can start by searching online for tutorials about "Bitcoin self custody".
There are many options available, some more practical for you, and some more practical for others. Don't spend too much time trying to find the perfect solution; practice and learn. You may make mistakes along the way, so be careful not to experiment with large amounts of your bitcoin as you explore new ideas and technologies along the way. This is similar to learning anything, like riding a bicycle; you are sure to fall a few times, scuff the frame, so don't buy a high performance racing bike while you're still learning to balance.
-
 @ 26d4b5b2:96393e73
2025-05-11 21:43:01
@ 26d4b5b2:96393e73
2025-05-11 21:43:01https://app.doh.money http://localhost:3000 https://dohmoney-cyxe-cyxeio-cyxecyxeios-projects.vercel.app GET POST OPTIONS PUT DELETE Content-Type Ocp-Apim-Subscription-Key Authorization Accept X-Requested-With X-Verified-By Content-Length Request-Context Date @(context.Request.Headers.GetValueOrDefault("Ocp-Apim-Subscription-Key", "50922ff015c14a84a092b4764dc6dddf")) @(context.Request.Headers.GetValueOrDefault("Origin", "https://app.doh.money")) @(context.Request.Headers.GetValueOrDefault("Origin", "http://localhost:3000")) GET, POST, OPTIONS, PUT, DELETE Content-Type, Ocp-Apim-Subscription-Key, Authorization, Accept, X-Requested-With,X-Verified-By Content-Length, Request-Context, Date @(context.Request.Headers.GetValueOrDefault("Origin", "https://app.doh.money")) @(context.Request.Headers.GetValueOrDefault("Origin", "http://localhost:3000")) GET, POST, OPTIONS, PUT, DELETE Content-Type, Ocp-Apim-Subscription-Key, Authorization, Accept, X-Requested-With, X-Verified-By Content-Length, Request-Context, Date -
 @ bf47c19e:c3d2573b
2025-05-11 18:23:13
@ bf47c19e:c3d2573b
2025-05-11 18:23:1305.12.2024 / Autor: Katarina Plantak
Vrijednost Bitcoina po prvi put je premašila 100.000 dolara. Ova kriptovaluta svoj masovni rast može na neki način zahvaliti reizboru Donalda Trumpa za američkog predsjednika. On je najavio blaži regulatorni pristup kripto industriji.
Što je Bitcoin?
Bitcoin (BTC) je kriptovaluta (virtualna valuta) dizajnirana da djeluje kao novac i oblik plaćanja izvan kontrole bilo koje osobe, grupe ili entiteta. Time nema potrebe za sudjelovanjem pouzdane treće strane npr. kovnice novca ili banke u financijskim transakcijama. Osoba ili grupa pod pseudonimom Satoshi Nakamoto 31. listopada 2008. objavila je tehnički dokument pod nazivom "Bitcoin: Peer-to-Peer Electronic Cash System". Taj je dokument distribuiran na kriptografsku mailing listu, samo mjesec dana nakon što je investicijska banka Lehman Brothers podnijela zahtjev za najveći bankrot u povijesti SAD-a, a vlada odobrila financijsku pomoć od 700 milijardi dolara.
Nekoliko mjeseci kasnije, 3. siječnja 2009., Bitcoin mreža pokrenula se, uvodeći novi sustav decentralizirane digitalne valute bez središnjeg posrednika.
Tko su osnivači Bitcoina?
Bitcoin je rezultat desetljeća razvoja kriptografije i ideja Cypherpunka iz 1970-ih, s projektima poput B-money, Bit Gold, eCash i HashCash.
Godine 2006., osoba ili grupa pod pseudonimom Satoshi Nakamoto započela je rad na Bitcoinu. Iako su kriptografi poput Hal Finneya, Nicka Szaba, Weija Daija i Adama Backa povezivani sa Satoshijem, svi su to negirali.
Satoshi je surađivao s programerima do 2010., kada je predao kontrolu nad izvornim kodom i 2011. nestao iz javnosti. Danas stotine programera razvijaju Bitcoin, koji ima zajednicu od milijun korisnika.
Kako funkcionira Bitcoin?
Bitcoin se može brzo i sigurno prenijeti na svakoga s Bitcoin adresom poput računa bilo gdje u svijetu, bez potrebe za dopuštenjem ili plaćanjem nepotrebnih naknada. BTC je jedinica valute u Bitcoin sustavu za koju postoji ograničena količina od 21 milijun. Svaki je Bitcoin djeljiv na 100 milijuna "satoshis" ili "sats" – najmanja jedinica Bitcoina, poput centa u dolaru. Bitcoini djeluju kao elektronički novac, omogućujući vam da izvršite plaćanje s univerzalnom valutom bilo gdje. Nalazi se u tzv. novčanicima u digitalnoj verziji. On funkcionira slično kao bankovni račun. Transakcije su moguće zahvaljujući peer-to-peer mreži. Osigurane su sustavom kriptografije javnog i privatnog ključa, objašnjava Kriptomat.
Bitcoin koristi kriptografiju javnog i privatnog ključa za sigurne transakcije. Javna adresa, izvedena iz "hasha" javnog ključa, koristi se za primanje sredstava. Privatni ključ služi kao digitalni potpis odnosno svojevrsna lozinka za autorizaciju transakcija i omogućava pristup sredstvima, pa ga treba čuvati u tajnosti.
Korisnik pokreće transakciju unosom javne adrese primatelja u svoj novčanik. Novčanik koristi privatni ključ za stvaranje digitalnog potpisa, čime se transakcija ovjerava i šalje na Bitcoin mrežu. Transakcija prvo ulazi u "mempool", gdje čeka potvrdu. Svakih desetak minuta, transakcije se grupiraju u blokove, koji se dodaju na blockchain, stvarajući neprekinuti lanac sigurnih zapisa.
Sigurnost sustava je toliko snažna da bi hakiranje jedne adrese trajalo milijardama godina.
Blockchain
Bitcoin je revolucionarno riješio problem dvostruke potrošnje, omogućujući prijenos sredstava izravno između korisnika bez posrednika. Zamislite mrežu stranaca, gdje svaki vodi vlastitu knjigu računa. Kada netko prenese 1 BTC, svi zapisuju transakciju i uspoređuju bilješke. Ako se sve podudaraju, transakcija se potvrđuje. Ako netko pokuša prevariti, njegova bilješka se odbacuje.
Ovaj sustav knjiga računa, distribuiran na globalnoj mreži, čini osnovu Bitcoin blockchaina. Svaki čvor ima identičnu kopiju koja javno i pseudonimno bilježi sve transakcije, osiguravajući točnost i sigurnost bez potrebe za skupim posrednicima.
Zašto je Bitcoin jedinstven i što mu daje vrijednost?
Bitcoin je revolucionirao digitalni novac stvaranjem decentraliziranog, sigurnog i otpornog sustava bez potrebe za posrednicima. Njegov kod omogućuje daljnje inovacije, a povremeno dolazi do "račvanja" koje stvara nove kriptovalute temeljene na Bitcoinu, iako one nikada ne mogu biti isti Bitcoin.
Njegova ključna snaga leži u decentralizaciji – nema središnje figure niti točke neuspjeha. Bitcoin se pokazao kao otporan na izazove, uključujući državne zabrane i snažna račvanja, što dodatno učvršćuje njegovu dugovječnost prema Lindyjevom efektu. Mrežni učinak potiče sve više korisnika da ga prihvate kao sredstvo za pohranu vrijednosti i razmjenu.
Njegova ograničena ponuda od 21 milijun BTC-a stvara oskudicu, čime se suprotstavlja inflacijskim valutama. Bitcoin je zamjenjiv, djeljiv na 100 milijuna dijelova, izdržljiv i prenosiv, što ga čini praktičnijim od zlata. S rastućim prihvaćanjem od strane tvrtki diljem svijeta, njegova vrijednost i korisnost nastavljaju rasti.
Blokovi, rudarenje i nagrade
Prvi Bitcoinblock izrudiran je 3. siječnja 2009. godine. Nazvan je Blok 0. Rudarenje Bitcoina je utrka između rudara za raspršivanje specifičnih vrijednosti i drugih informacija o bloku kako bi se pronašlo rješenje za problem raspršivanja i dodalo blok u blockchain. Pobjednički rudar nagrađen je Bitcoinima. Bitcoin nagrade se prepolovljuju svakih 210.000 blokova. Na primjer, nagrada za blok bila je 50 novih bitcoina u 2009. godini, a 11. svibnja 2020. kad se dogodilo treće prepolovljenje nagrada za svaki blok smanjena je na 6.25 bitcoina. Četvrto prepolovljenje dogodilo se u travnju 2024. i smanjilo je nagradu na 3.125 Bitcoina. Sljedeće prepolovljavanje trebalo bi se dogoditi sredinom 2028. i smanjiti nagradu na 1.5625 BTC.
Do 2140. godine, nakon 32. prepolovljenja, nagrada za rudarenje Bitcoina smanjit će se na nulu, dosegnuvši ukupnu ponudu od 21 milijun BTC-a. Tada će se rudari oslanjati isključivo na naknade za transakcije kako bi pokrili svoje troškove.
Svako prepolovljenje smanjuje količinu novih BTC-a, što povijesno dovodi do porasta cijene zbog smanjene ponude i povećane potražnje. Iako će se učinak budućih prepolovljenja možda smanjivati zbog sve manjih količina nove ponude, do sada su ta prepolovljenja bila ključni pokretači triju glavnih tržišnih ciklusa Bitcoina.
