-
 @ 348e7eb2:3b0b9790
2025-05-24 05:00:33
@ 348e7eb2:3b0b9790
2025-05-24 05:00:33Nostr-Konto erstellen - funktioniert mit Hex
Was der Button macht
Der folgende Code fügt einen Button hinzu, der per Klick einen Nostr-Anmeldedialog öffnet. Alle Schritte sind im Code selbst ausführlich kommentiert.
```html
```
Erläuterungen:
- Dynamisches Nachladen: Das Script
modal.jswird nur bei Klick nachgeladen, um Fehlermeldungen beim Initial-Load zu vermeiden. -
Parameter im Überblick:
-
baseUrl: Quelle für API und Assets. an: App-Name für den Modal-Header.aa: Farbakzent (Foerbico-Farbe als Hex).al: Sprache des Interfaces.am: Licht- oder Dunkelmodus.afb/asb: Bunker-Modi für erhöhten Datenschutz.aan/aac: Steuerung der Rückgabe privater Schlüssel.arr/awr: Primal Relay als Lese- und Schreib-Relay.-
Callbacks:
-
onComplete: Schließt das Modal, zeigt eine Bestätigung und bietet die Weiterleitung zu Primal an. onCancel: Schließt das Modal und protokolliert den Abbruch.
Damit ist der gesamte Code sichtbar, kommentiert und erklärt.
- Dynamisches Nachladen: Das Script
-
 @ 21335073:a244b1ad
2025-05-21 16:58:36
@ 21335073:a244b1ad
2025-05-21 16:58:36The other day, I had the privilege of sitting down with one of my favorite living artists. Our conversation was so captivating that I felt compelled to share it. I’m leaving his name out for privacy.
Since our last meeting, I’d watched a documentary about his life, one he’d helped create. I told him how much I admired his openness in it. There’s something strange about knowing intimate details of someone’s life when they know so little about yours—it’s almost like I knew him too well for the kind of relationship we have.
He paused, then said quietly, with a shy grin, that watching the documentary made him realize how “odd and eccentric” he is. I laughed and told him he’s probably the sanest person I know. Because he’s lived fully, chasing love, passion, and purpose with hardly any regrets. He’s truly lived.
Today, I turn 44, and I’ll admit I’m a bit eccentric myself. I think I came into the world this way. I’ve made mistakes along the way, but I carry few regrets. Every misstep taught me something. And as I age, I’m not interested in blending in with the world—I’ll probably just lean further into my own brand of “weird.” I want to live life to the brim. The older I get, the more I see that the “normal” folks often seem less grounded than the eccentric artists who dare to live boldly. Life’s too short to just exist, actually live.
I’m not saying to be strange just for the sake of it. But I’ve seen what the crowd celebrates, and I’m not impressed. Forge your own path, even if it feels lonely or unpopular at times.
It’s easy to scroll through the news and feel discouraged. But actually, this is one of the most incredible times to be alive! I wake up every day grateful to be here, now. The future is bursting with possibility—I can feel it.
So, to my fellow weirdos on nostr: stay bold. Keep dreaming, keep pushing, no matter what’s trending. Stay wild enough to believe in a free internet for all. Freedom is radical—hold it tight. Live with the soul of an artist and the grit of a fighter. Thanks for inspiring me and so many others to keep hoping. Thank you all for making the last year of my life so special.
-
 @ 06830f6c:34da40c5
2025-05-24 04:21:03
@ 06830f6c:34da40c5
2025-05-24 04:21:03The evolution of development environments is incredibly rich and complex and reflects a continuous drive towards greater efficiency, consistency, isolation, and collaboration. It's a story of abstracting away complexity and standardizing workflows.
Phase 1: The Bare Metal & Manual Era (Early 1970s - Late 1990s)
-
Direct OS Interaction / Bare Metal Development:
- Description: Developers worked directly on the operating system's command line or a basic text editor. Installation of compilers, interpreters, and libraries was a manual, often arcane process involving downloading archives, compiling from source, and setting environment variables. "Configuration drift" (differences between developer machines) was the norm.
- Tools: Text editors (Vi, Emacs), command-line compilers (GCC), Makefiles.
- Challenges: Extremely high setup time, dependency hell, "works on my machine" syndrome, difficult onboarding for new developers, lack of reproducibility. Version control was primitive (e.g., RCS, SCCS).
-
Integrated Development Environments (IDEs) - Initial Emergence:
- Description: Early IDEs (like Turbo Pascal, Microsoft Visual Basic) began to integrate editors, compilers, debuggers, and sometimes GUI builders into a single application. This was a massive leap in developer convenience.
- Tools: Turbo Pascal, Visual Basic, early Visual Studio versions.
- Advancement: Improved developer productivity, streamlined common tasks. Still relied on local system dependencies.
Phase 2: Towards Dependency Management & Local Reproducibility (Late 1990s - Mid-2000s)
-
Basic Build Tools & Dependency Resolvers (Pre-Package Managers):
- Description: As projects grew, manual dependency tracking became impossible. Tools like Ant (Java) and early versions of
autoconf/makefor C/C++ helped automate the compilation and linking process, managing some dependencies. - Tools: Apache Ant, GNU Autotools.
- Advancement: Automated build processes, rudimentary dependency linking. Still not comprehensive environment management.
- Description: As projects grew, manual dependency tracking became impossible. Tools like Ant (Java) and early versions of
-
Language-Specific Package Managers:
- Description: A significant leap was the emergence of language-specific package managers that could fetch, install, and manage libraries and frameworks declared in a project's manifest file. Examples include Maven (Java), npm (Node.js), pip (Python), RubyGems (Ruby), Composer (PHP).
- Tools: Maven, npm, pip, RubyGems, Composer.
- Advancement: Dramatically simplified dependency resolution, improved intra-project reproducibility.
- Limitation: Managed language-level dependencies, but not system-level dependencies or the underlying OS environment. Conflicts between projects on the same machine (e.g., Project A needs Python 2.7, Project B needs Python 3.9) were common.
Phase 3: Environment Isolation & Portability (Mid-2000s - Early 2010s)
-
Virtual Machines (VMs) for Development:
- Description: To address the "it works on my machine" problem stemming from OS-level and system-level differences, developers started using VMs. Tools like VMware Workstation, VirtualBox, and later Vagrant (which automated VM provisioning) allowed developers to encapsulate an entire OS and its dependencies for a project.
- Tools: VMware, VirtualBox, Vagrant.
- Advancement: Achieved strong isolation and environment reproducibility (a true "single environment" for a project).
- Limitations: Resource-heavy (each VM consumed significant CPU, RAM, disk space), slow to provision and boot, difficult to share large VM images.
-
Early Automation & Provisioning Tools:
- Description: Alongside VMs, configuration management tools started being used to automate environment setup within VMs or on servers. This helped define environments as code, making them more consistent.
- Tools: Chef, Puppet, Ansible.
- Advancement: Automated provisioning, leading to more consistent environments, often used in conjunction with VMs.
Phase 4: The Container Revolution & Orchestration (Early 2010s - Present)
-
Containerization (Docker):
- Description: Docker popularized Linux Containers (LXC), offering a lightweight, portable, and efficient alternative to VMs. Containers package an application and all its dependencies into a self-contained unit that shares the host OS kernel. This drastically reduced resource overhead and startup times compared to VMs.
- Tools: Docker.
- Advancement: Unprecedented consistency from development to production (Dev/Prod Parity), rapid provisioning, highly efficient resource use. Became the de-facto standard for packaging applications.
-
Container Orchestration:
- Description: As microservices and container adoption grew, managing hundreds or thousands of containers became a new challenge. Orchestration platforms automated the deployment, scaling, healing, and networking of containers across clusters of machines.
- Tools: Kubernetes, Docker Swarm, Apache Mesos.
- Advancement: Enabled scalable, resilient, and complex distributed systems development and deployment. The "environment" started encompassing the entire cluster.
Phase 5: Cloud-Native, Serverless & Intelligent Environments (Present - Future)
-
Cloud-Native Development:
- Description: Leveraging cloud services (managed databases, message queues, serverless functions) directly within the development workflow. Developers focus on application logic, offloading infrastructure management to cloud providers. Containers become a key deployment unit in this paradigm.
- Tools: AWS Lambda, Azure Functions, Google Cloud Run, cloud-managed databases.
- Advancement: Reduced operational overhead, increased focus on business logic, highly scalable deployments.
-
Remote Development & Cloud-Based IDEs:
- Description: The full development environment (editor, terminal, debugger, code) can now reside in the cloud, accessed via a thin client or web browser. This means developers can work from any device, anywhere, with powerful cloud resources backing their environment.
- Tools: GitHub Codespaces, Gitpod, AWS Cloud9, VS Code Remote Development.
- Advancement: Instant onboarding, consistent remote environments, access to high-spec machines regardless of local hardware, enhanced security.
-
Declarative & AI-Assisted Environments (The Near Future):
- Description: Development environments will become even more declarative, where developers specify what they need, and AI/automation tools provision and maintain it. AI will proactively identify dependency issues, optimize resource usage, suggest code snippets, and perform automated testing within the environment.
- Tools: Next-gen dev container specifications, AI agents integrated into IDEs and CI/CD pipelines.
- Prediction: Near-zero environment setup time, self-healing environments, proactive problem identification, truly seamless collaboration.
web3 #computing #cloud #devstr
-
-
 @ 51bbb15e:b77a2290
2025-05-21 00:24:36
@ 51bbb15e:b77a2290
2025-05-21 00:24:36Yeah, I’m sure everything in the file is legit. 👍 Let’s review the guard witness testimony…Oh wait, they weren’t at their posts despite 24/7 survellience instructions after another Epstein “suicide” attempt two weeks earlier. Well, at least the video of the suicide is in the file? Oh wait, a techical glitch. Damn those coincidences!
At this point, the Trump administration has zero credibility with me on anything related to the Epstein case and his clients. I still suspect the administration is using the Epstein files as leverage to keep a lot of RINOs in line, whereas they’d be sabotaging his agenda at every turn otherwise. However, I just don’t believe in ends-justify-the-means thinking. It’s led almost all of DC to toss out every bit of the values they might once have had.
-
 @ c9badfea:610f861a
2025-05-20 19:49:20
@ c9badfea:610f861a
2025-05-20 19:49:20- Install Sky Map (it's free and open source)
- Launch the app and tap Accept, then tap OK
- When asked to access the device's location, tap While Using The App
- Tap somewhere on the screen to activate the menu, then tap ⁝ and select Settings
- Disable Send Usage Statistics
- Return to the main screen and enjoy stargazing!
ℹ️ Use the 🔍 icon in the upper toolbar to search for a specific celestial body, or tap the 👁️ icon to activate night mode
-
 @ 90152b7f:04e57401
2025-05-24 03:47:24
@ 90152b7f:04e57401
2025-05-24 03:47:24"Army study suggests U.S. force of 20,000"
The Washington Times - Friday, April 5, 2002
The Bush administration says there are no active plans to put American peacekeepers between Palestinians and Israelis, but at least one internal military study says 20,000 well-armed troops would be needed.
The Army’s School of Advanced Military Studies (SAMS), an elite training ground and think tank at Fort Leavenworth, Kan., produced the study last year. The 68-page paper tells how the major operation would be run the first year, with peacekeepers stationed in Gaza, Hebron, Jerusalem and Nablus.
One major goal would be to “neutralize leadership of Palestine dissenting factions [and] prevent inter-Palestinian violence.”
The military is known to update secret contingency plans in the event international peacekeepers are part of a comprehensive Middle East peace plan. The SAMS study, a copy of which was obtained by The Washington Times, provides a glimpse of what those plans might entail.
Defense Secretary Donald H. Rumsfeld repeatedly has said the administration has no plans to put American troops between the warring factions. But since the escalation of violence, more voices in the debate are beginning to suggest that some type of American-led peace enforcement team is needed.
Sen. Arlen Specter, Pennsylvania Republican, quoted U.S. special envoy Gen. Anthony Zinni as saying there is a plan, if needed, to put a limited number of American peacekeepers in the Israeli-occupied territories.
Asked on CBS whether he could envision American troops on the ground, Mr. Specter said Sunday: “If we were ever to stabilize the situation, and that was a critical factor, it’s something that I would be willing to consider.”
Added Sen. Joseph R. Biden Jr., Delaware Democrat and Senate Foreign Relations Committee chairman, “In that context, yes, and with European forces as well.”
The recent history of international peacekeeping has shown that it often takes American firepower and prestige for the operation to work. The United Nations made futile attempts to stop Serbian attacks on the Muslim population in Bosnia.
The U.S. entered the fray by bombing Serbian targets and bringing about a peace agreement that still is being backed up by American soldiers on the ground. U.S. combat troops are also in Kosovo, and they have a more limited role in Macedonia.
But James Phillips, a Middle East analyst at the Heritage Foundation, used the word “disaster” to describe the aftermath of putting an international force in the occupied territories.
“I think that would be a formula for sucking us into the violence,” he said. “United States troops would be a lightening rod for attacks by radical Islamics and other Palestinian extremist groups. The United States cannot afford to stretch its forces any thinner. They’re very busy as it is with the war against international terrorism.”
Mr. Phillips noted that two Norwegian observers in Hebron were killed this week. U.N. representatives on the Lebanon border have been unable to prevent terrorists from attacking Israel.
The SAMS paper tries to predict events in the first year of peacekeeping and the dangers U.S. troops would face.
It calls the Israeli armed forces a “500-pound gorilla in Israel. Well armed and trained. Operates in both Gaza [and the West Bank]. Known to disregard international law to accomplish mission. Very unlikely to fire on American forces.”
On the Mossad, the Israeli intelligence service, the Army study says, “Wildcard. Ruthless and cunning. Has capability to target U.S. forces and make it look like a Palestinian/Arab act.”
It described Palestinian youth as “loose cannons; under no control, sometimes violent.” The study was done by 60 officers dubbed the “Jedi Knights,” as all second-year SAMS students are called. The Times first reported on their work in September. Recent violence in the Middle East has raised questions about what type of force it would take to keep the peace.
In the past, SAMS has done studies for the Army chief of staff and the Joint Chiefs. SAMS personnel helped plan the allied ground attack that liberated Kuwait.
The Middle East study sets goals that a peace force should accomplish in the first 30 days. They include “create conditions for development of Palestinian State and security of [Israel],” ensure “equal distribution of contract value or equivalent aid” and “build lasting relationships based on new legal borders and not religious-territorial claims.”
The SAMS report does not specify a full order of battle for the 20,000 troops. An Army source who reviewed the paper said each of three brigades would require about 100 armored vehicles, 25 tanks and 12 self-propelled howitzers, along with attack helicopters and spy drones.
The Palestinians have supported calls for an international force, but Tel Aviv has opposed the idea.
https://www.washingtontimes.com/news/2002/apr/5/20020405-041726-2086r/
-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 2b998b04:86727e47
2025-05-24 03:40:36
@ 2b998b04:86727e47
2025-05-24 03:40:36Solzhenitsyn Would Have Loved Bitcoin
I didn’t plan to write this. But a comment from @HODL stirred something in me — a passing thought that took root and wouldn’t let go:
> “Solzhenitsyn would have understood Bitcoin.”
The more I sat with it, the more I realized: he wouldn’t have just understood it — he would have loved it.
A Life of Resistance
Aleksandr Solzhenitsyn didn’t just survive the Soviet gulags — he exposed them. Through The Gulag Archipelago and other works, he revealed the quiet machinery of evil: not always through brutality, but through systemic lies, suppressed memory, and coerced consensus.
His core belief was devastatingly simple:
> “The line dividing good and evil cuts through the heart of every human being.”
He never let anyone off the hook — not the state, not the system, not even himself. Evil, to Solzhenitsyn, was not “out there.” It was within. And resisting it required truth, courage, and deep personal responsibility.
Bitcoin: Truth That Resists
That’s why I believe Solzhenitsyn would have resonated with Bitcoin.
Not the hype. Not the coins. Not the influencers.
But the heart of it:
-
A system that resists coercion.
-
A ledger that cannot be falsified.
-
A network that cannot be silenced.
-
A protocol that doesn't care about party lines — only proof of work.
Bitcoin is incorruptible memory.\ Solzhenitsyn fought to preserve memory in the face of state erasure.\ Bitcoin cannot forget — and it cannot be made to lie.
Responsibility and Sovereignty
Bitcoin demands what Solzhenitsyn demanded: moral responsibility. You hold your keys. You verify your truth. You cannot delegate conscience.
He once wrote:
> “A man who is not inwardly prepared for the use of violence against him is always weaker than his opponent.”
Bitcoin flips that equation. It gives the peaceful man a weapon: truth that cannot be seized.
I’ve Felt This Line Too
I haven’t read all of The Gulag Archipelago — it’s long, and weighty — but I’ve read enough to know Solzhenitsyn’s voice. And I’ve felt the line he describes:
> That dividing line between good and evil… that runs through my own heart.
That’s why I left the noise of Web3. That’s why I’m building with Bitcoin. Because I believe the moral architecture of this protocol matters. It forces me to live in alignment — or walk away.
Final Word
I think Solzhenitsyn would have seen Bitcoin not as a tech innovation, but as a moral stand. Not a replacement for Christ — but a quiet echo of His justice.
And that’s why I keep stacking, writing, building — one block at a time.
Written with help from ChatGPT (Dr. C), and inspired by a comment from @HODL that sparked something deep.
If this resonated, feel free to zap a few sats — not because I need them, but because signal flows best when it’s shared with intention.
HODL mentioned this idea in a note — their Primal profile:\ https://primal.net/hodl
-
-
 @ 58537364:705b4b85
2025-05-24 03:25:05
@ 58537364:705b4b85
2025-05-24 03:25:05Ep 228 "วิชาชีวิต"
คนเราเมื่อเกิดมาแล้ว ไม่ได้หวังแค่มีชีวิตรอดเท่านั้น แต่ยังปรารถนา "ความเจริญก้าวหน้า" และ "ความสุขในชีวิต"
จึงพากันศึกษาเล่าเรียนเพื่อให้มี "วิชาความรู้" สำหรับการประกอบอาชีพ โดยเชื่อว่า การงานที่มั่นคงย่อมนำ "ความสำเร็จ" และ "ความเจริญก้าวหน้า" มาให้
อย่างไรก็ตาม...ความสำเร็จในวิชาชีพหรือความเจริญก้าวหน้าในชีวิต ไม่ได้เป็นหลักประกันความสุขอย่างแท้จริง
แม้เงินทองและทรัพย์สมบัติจะช่วยให้ชีวิตมีความสุข สะดวก สบาย แต่ไม่ได้ช่วยให้สุขใจในสิ่งที่ตนมี หากยังรู้สึกว่า "ตนยังมีไม่พอ"
ขณะเดียวกันชื่อเสียงเกียรติยศที่ได้มาก็ไม่ช่วยให้คลายความทุกข์ใจ เมื่อต้องเผชิญปัญหาต่างๆ นาๆ
ทั้งการพลัดพราก การสูญเสียบุคคลผู้เป็นที่รัก ความเจ็บป่วย และความตายที่ต้องเกิดขึ้นกับทุกคน
ยิ่งกว่านั้น...ความสำเร็จในอาชีพและความเจริญก้าวหน้าในชีวิต ล้วนเป็น "สิ่งไม่เที่ยง" แปรผันตกต่ำ ไม่สามารถควบคุมได้
วิชาชีพทั้งหลายช่วยให้เราหาเงินได้มากขึ้น แต่ไม่ได้ช่วยให้เราเข้าถึง "ความสุขที่แท้จริง"
คนที่ประสบความสำเร็จในวิชาชีพไม่น้อย ที่มีชีวิตอมทุกข์ ความเครียดรุมเร้า สุขภาพเสื่อมโทรม
หากเราไม่อยากเผชิญกับสิ่งเหล่านี้ ควรเรียน "วิชาชีวิต" เพื่อเข้าใจโลก เข้าใจชีวิต รู้เท่าทันความผันแปรไปของสรรพสิ่ง
วิชาชีวิต...เรียนจากประสบการณ์ชีวิต เมื่อมีปัญหาต่างๆ ขอให้คิดว่า คือ "บททดสอบ"
จงหมั่นศึกษาหาบทเรียนจากวิชานี้อยู่เสมอ สร้าง "ความตระหนักรู้" ถึงความสำคัญในการมีชีวิต
ช่วงที่ผ่านมา เมื่อมีปัญหาฉันไม่สามารถหาทางออกจากทุกข์ได้เศร้า เสียใจ ทุรน ทุราย สอบตก "วิชาชีวิต"
โชคดีครูบาอาจารย์ให้ข้อคิด กล่าวว่า เป็นเรื่องธรรมดาหากเรายังไม่เข้าใจชีวิต ทุกสิ่งล้วนผันแปร เกิด-ดับ เป็นธรรมดา ท่านเมตตาส่งหนังสือเล่มนี้มาให้
เมื่อค่อยๆ ศึกษา ทำความเข้าใจ นำความทุกข์ที่เกิดขึ้นมาพิจารณา เห็นว่าเมื่อ "สอบตก" ก็ "สอบใหม่" จนกว่าจะผ่านไปได้
วิชาทางโลกเมื่อสอบตกยังเปิดโอกาสให้เรา "สอบซ่อม" วิชาทางธรรมก็เช่นเดียวกัน หากเจอปัญหา อุปสรรค หรือ ความทุกข์ถาโถมเข้ามา ขอให้เราตั้งสติ ว่า จะตั้งใจทำข้อสอบนี้ให้ผ่านไปให้จงได้
หากเราสามารถดำเนินชีวิตด้วยความเข้าใจ เราจะค้นพบ "วิชาชีวิต" ที่สามารถทำให้หลุดพ้นจากความทุกข์ได้แน่นอน
ด้วยรักและปรารถนาดี ปาริชาติ รักตะบุตร 21 เมษายน 2566
น้อมกราบขอบพระคุณพระ อ.ไพศาล วิสาโล เป็นอย่างสูง ที่ท่านเมตตา ให้ข้อธรรมะยามทุกข์ใจและส่งหนังสือมาให้ จึงตั้งใจอยากแบ่งปันเป็นธรรมทาน
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 2b998b04:86727e47
2025-05-24 03:16:38
@ 2b998b04:86727e47
2025-05-24 03:16:38Most of the assets I hold—real estate, equities, and businesses—depreciate in value over time. Some literally, like physical buildings and equipment. Some functionally, like tech platforms that age faster than they grow. Even cash, which should feel "safe," quietly loses ground to inflation. Yet I continue to build. I continue to hold. And I continue to believe that what I’m doing matters.
But underneath all of that — beneath the mortgages, margin trades, and business pivots — I’ve made a long-term bet:
Bitcoin will outlast the decay.
The Decaying System I Still Operate In
Let me be clear: I’m not a Bitcoin purist. I use debt. I borrow to acquire real estate. I trade with margin in a brokerage account. I understand leverage — not as a sin, but as a tool that must be used with precision and respect. But I’m also not naive.
The entire fiat-based financial system is built on a slow erosion of value. Inflation isn't a bug — it’s a feature. And it's why most business models, whether in real estate or retail, implicitly rely on asset inflation just to stay solvent.
That’s not sustainable. And it’s not honest.
The Bitcoin Thesis: Deflation That Works for You
Bitcoin is fundamentally different. Its supply is fixed. Its issuance is decreasing. Over time, as adoption grows and fiat weakens, Bitcoin’s purchasing power increases.
That changes the game.
If you can hold even a small portion of your balance sheet in BTC — not just as an investment, but as a strategic hedge — it becomes a way to offset the natural depreciation of your other holdings. Your buildings may age. Your cash flow may fluctuate. But your Bitcoin, if properly secured and held with conviction, becomes the anchor.
It’s not about day trading BTC or catching the next ATH. It’s about understanding that in a world designed to leak value, Bitcoin lets you patch the hole.
Why This Matters for Builders
If you run a business — especially one with real assets, recurring costs, or thin margins — you know how brutal depreciation can be. Taxes, maintenance, inflation, replacement cycles… it never stops.
Adding BTC to your long-term treasury isn’t about becoming a "crypto company." It’s about becoming anti-fragile. It’s about building with a component that doesn’t rot.
In 5, 10, or 20 years, I may still be paying off mortgages and navigating property cycles. But if my Bitcoin allocation is still intact, still growing in real purchasing power… then I haven’t just preserved wealth. I’ve preserved optionality. I’ve created a counterbalance to the relentless decay of everything else.
Final Word
I still play the fiat game — because for now, I have to. But I’m no longer betting everything on it. Bitcoin is my base layer now. Quiet, cold-stored, and uncompromising.
It offsets depreciation — not just financially, but philosophically. It reminds me that not everything has to erode. Not everything has to be sacrificed to time or policy or inflation.
Some things can actually hold. Some things can last.
And if I build right — maybe what I build can last too.
If this resonated, feel free to send a zap — it helps me keep writing and building from a place of conviction.
This article was co-written with the help of ChatGPT, a tool I use to refine and clarify what I’m working through in real time.
-
 @ 502ab02a:a2860397
2025-05-24 01:14:43
@ 502ab02a:a2860397
2025-05-24 01:14:43ในสายตาคนรักสุขภาพทั่วโลก “อโวคาโด” คือผลไม้ในฝัน มันมีไขมันดี มีไฟเบอร์สูง ช่วยลดคอเลสเตอรอลได้ มีวิตามินอี มีโพแทสเซียม และที่สำคัญคือ "ดูดี" ทุกครั้งที่ถูกปาดวางบนขนมปังโฮลวีตในชามสลัด หรือบนโฆษณาอาหารคลีนสุดหรู
แต่ในสายตาชาวไร่บางคนในเม็กซิโกหรือชุมชนพื้นเมืองในโดมินิกัน อโวคาโดไม่ใช่ผลไม้แห่งสุขภาพ แต่มันคือสัญลักษณ์ของความรุนแรง การกดขี่ และการสูญเสียเสรีภาพในผืนดินของตัวเอง
เมื่ออาหารกลายเป็นทองคำ กลุ่มอิทธิพลก็ไม่เคยพลาดจะเข้าครอบครอง
เรามักได้ยินคำว่า "ทองคำเขียว" หรือ Green Gold ใช้เรียกอโวคาโด เพราะในรอบ 20 ปีที่ผ่านมา ความต้องการบริโภคของมันพุ่งสูงขึ้นเป็นเท่าตัว โดยเฉพาะในสหรัฐฯ และยุโรป จากผลการวิจัยของมหาวิทยาลัยฮาร์วาร์ดและข้อมูลการส่งออกของ USDA พบว่า 90% ของอโวคาโดที่บริโภคในอเมริกา มาจากรัฐมิโชอากังของเม็กซิโก พื้นที่ซึ่งควบคุมโดยกลุ่มค้ายาเสพติดไม่ต่างจากเจ้าของสวนตัวจริง
พวกเขาเรียกเก็บ “ค่าคุ้มครอง” จากเกษตรกร โดยใช้วิธีเดียวกับมาเฟีย คือ ถ้าไม่จ่าย ก็เจ็บตัวหรือหายตัว ไม่ว่าจะเป็นกลุ่ม CJNG (Jalisco New Generation Cartel), Familia Michoacana หรือ Caballeros Templarios พวกเขาไม่ได้สนใจว่าใครปลูกหรือใครรดน้ำ ตราบใดที่ผลผลิตสามารถเปลี่ยนเป็นเงินได้
องค์กรอาชญากรรมเหล่านี้ไม่ได้แค่ “แฝงตัว” ในอุตสาหกรรม แต่ ยึดครอง ห่วงโซ่การผลิตทั้งหมด ตั้งแต่แปลงปลูกไปจนถึงโรงบรรจุและเส้นทางขนส่ง คนที่ไม่ยอมเข้าระบบมืดอาจต้องพบจุดจบในป่า หรือไม่มีชื่ออยู่ในทะเบียนบ้านอีกต่อไป
จากรายงานของเว็บไซต์ Food is Power องค์กรไม่แสวงกำไรด้านความยุติธรรมด้านอาหารในสหรัฐฯ เผยว่า ในปี 2020 มีเกษตรกรในเม็กซิโกจำนวนมากที่ถูกข่มขู่ บางรายถึงขั้นถูกฆาตกรรม เพราะปฏิเสธจ่ายค่าคุ้มครองจากกลุ่มค้ายา
การปลูกอโวคาโดไม่ใช่เรื่องเบาๆ กับธรรมชาติ เพราะมันต้องการ “น้ำ” มากถึง 272 ลิตรต่อผลเดียว! เรามาดูว่า “272 ลิตร” นี้ เท่ากับอะไรบ้างในชีวิตจริง อาบน้ำฝักบัวนาน 10–12 นาที (โดยเฉลี่ยใช้น้ำ 20–25 ลิตรต่อนาที) ใช้น้ำซักเสื้อผ้าเครื่องหนึ่ง (เครื่องซักผ้า 1 ครั้งกินประมาณ 60–100 ลิตร) น้ำดื่มของคนหนึ่งคนได้นานเกือบ เดือน (คนเราต้องการน้ำดื่มประมาณ 1.5–2 ลิตรต่อวัน)
ถ้าเราใช้ข้อมูลจาก FAO และ Water Footprint Network การผลิตเนื้อวัว 1 กิโลกรัม ต้องใช้น้ำ 15,000 ลิตร (รวมทั้งการปลูกหญ้า อาหารสัตว์ การดื่มน้ำของวัว ฯลฯ) ได้โปรตีนราว 250 กรัม อโวคาโด 1 กิโลกรัม (ราว 5 ผล) ใช้น้ำประมาณ 1,360 ลิตร ได้โปรตีนเพียง 6–8 กรัมเท่านั้น พูดง่ายๆคือ เมื่อเทียบอัตราส่วนเป็นลิตรต่อกรัมโปรตีนแล้วนั้น วัวใช้น้ำ 60 ลิตรต่อกรัมโปรตีน / อโวคาโด ใช้น้ำ 194 ลิตรต่อกรัมโปรตีน แถมการเลี้ยงวัวในระบบธรรมชาติ (เช่น pasture-raised หรือ regenerative farming) ยังสามารถเป็นส่วนหนึ่งของระบบหมุนเวียนน้ำและคาร์บอนได้ พอเห็นภาพแล้วใช่ไหมครับ ดังนั้นเราควรระมัดระวังการเสพสื่อเอาไว้ด้วยว่า คำว่า "ดีต่อโลก" ไม่ได้หมายถึงพืชอย่างเดียว ทุกธุรกิจถ้าทำแบบที่ควรทำ มันยังสามารถผลักดันโลกไม่ให้ตกอยู่ในมือองค์กร future food ได้ เพราะมูลค่ามันสูงมาก
และเมื่อราคาสูง พื้นที่เพาะปลูกก็ขยายอย่างไร้การควบคุม ป่าธรรมชาติในรัฐมิโชอากังถูกแอบโค่นแบบผิดกฎหมายเพื่อแปลงสภาพเป็นไร่ “ทองเขียว” ข้อมูลจาก Reuters พบว่าผลไม้ที่ถูกส่งออกไปยังสหรัฐฯ บางส่วนมาจากแปลงปลูกที่บุกรุกป่าคุ้มครอง และรัฐบาลเองก็ไม่สามารถควบคุมได้เพราะอิทธิพลของกลุ่มทุนและมาเฟีย
ในโดมินิกันก็เช่นกัน มีรายงานจากสำนักข่าว Gestalten ว่าพื้นที่ป่าสงวนหลายพันไร่ถูกเปลี่ยนเป็นไร่อโวคาโด เพื่อป้อนตลาดผู้บริโภคในอเมริกาและยุโรปโดยตรง โดยไม่มีการชดเชยใดๆ แก่ชุมชนท้องถิ่น
สุขภาพที่ดีไม่ควรได้มาจากการทำลายสุขภาพของคนอื่น ไม่ควรมีผลไม้ใดที่ดูดีในจานของเรา แล้วเบื้องหลังเต็มไปด้วยคราบเลือดและน้ำตาของคนปลูก
เฮียไม่ได้จะบอกให้เลิกกินอโวคาโดเลย แต่เฮียอยากให้เรารู้ทัน ว่าความนิยมของอาหารสุขภาพวันนี้ กำลังเป็นสนามใหม่ของกลุ่มทุนโลก ที่พร้อมจะครอบครองด้วย “อำนาจอ่อน” ผ่านแบรนด์อาหารธรรมชาติ ผ่านกฎหมายสิ่งแวดล้อม หรือแม้แต่การครอบงำตลาดเสรีด้วยกำลังอาวุธ
นี่ไม่ใช่เรื่องไกลตัว เพราะเมื่อกลุ่มทุนเริ่มฮุบเมล็ดพันธุ์ คุมเส้นทางขนส่ง คุมฉลาก Certified Organic ทั้งหลาย พวกเขาก็ “ควบคุมสุขภาพ” ของผู้บริโภคเมืองอย่างเราไปด้วยโดยอ้อม
คำถามสำคัญที่มาทุกครั้งเวลามีเนื้อหาอะไรมาฝากคือ แล้วเราจะทำอะไรได้? 555555 - เลือกบริโภคผลไม้จากแหล่งที่โปร่งใสหรือปลูกเองได้ - สนับสนุนเกษตรกรรายย่อยที่ไม่อยู่ภายใต้กลุ่มทุน - ใช้เสียงของผู้บริโภคกดดันให้มีระบบตรวจสอบต้นทางจริง ไม่ใช่แค่ฉลากเขียวสวยๆ - และที่สำคัญ อย่าเชื่อว่า “ทุกสิ่งที่เขาวางให้ดูสุขภาพดี” จะดีจริง (ข้อนี่ละตัวดีเลยครับ)
สุขภาพไม่ใช่สินค้า และอาหารไม่ควรเป็นอาวุธของกลุ่มทุน หากเราเริ่มตระหนักว่าอาหารคือการเมือง น้ำคืออำนาจ และแปลงเกษตรคือสนามรบ เฮียเชื่อว่าผู้บริโภคอย่างเราจะไม่ยอมเป็นหมากอีกต่อไป #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ 472f440f:5669301e
2025-05-20 13:01:09
@ 472f440f:5669301e
2025-05-20 13:01:09Marty's Bent

via me
Don't sleep on what's happening in Japan right now. We've been covering the country and the fact that they've lost control of their yield curve since late last year. After many years of making it a top priority from a monetary policy perspective, last year the Bank of Japan decided to give up on yield curve control in an attempt to reel inflation. This has sent yields for the 30-year and 40-year Japanese government bonds to levels not seen since the early 2000s in the case of the 30-year and levels never before seen for the 40-year, which was launched in 2007. With a debt to GDP ratio that has surpassed 250% and a population that is aging out with an insufficient amount of births to replace the aging workforce, it's hard to see how Japan can get out of this conundrum without some sort of economic collapse.
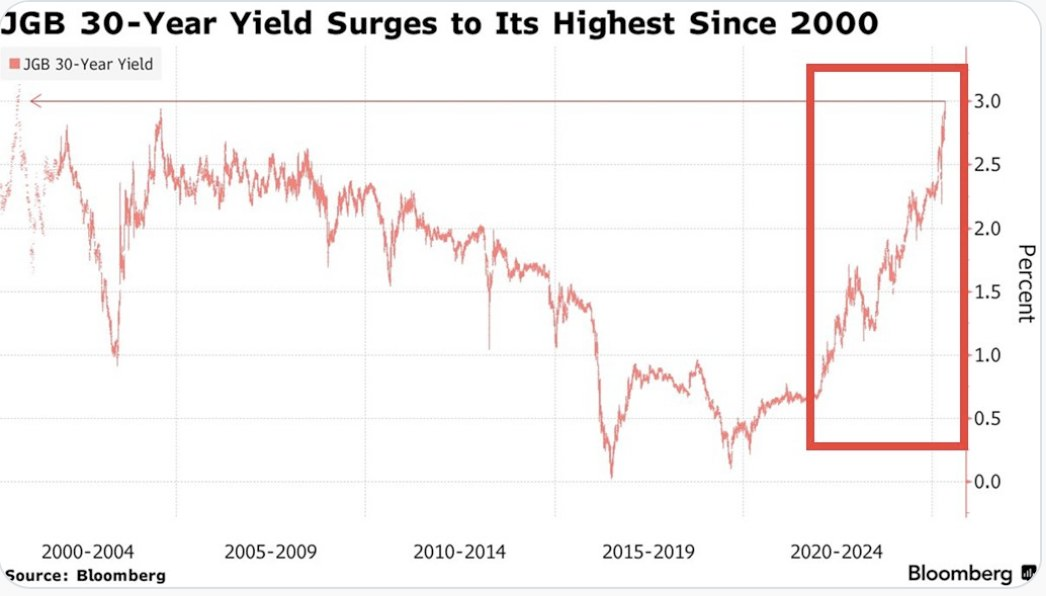

This puts the United States in a tough position considering the fact that Japan is one of the largest holders of U.S. Treasury bonds with more than 1,135 sats | $1.20 trillion in exposure. If things get too out of control in Japan and the yield curve continues to drift higher and inflation continues to creep higher Japan can find itself in a situation where it's a forced seller of US Treasuries as they attempt to strengthen the yen. Another aspect to consider is the fact that investors may see the higher yields on Japanese government bonds and decide to purchase them instead of US Treasuries. This is something to keep an eye on in the weeks to come. Particularly if higher rates drive a higher cost of capital, which leads to even more inflation. As producers are forced to increase their prices to ensure that they can manage their debt repayments.
It's never a good sign when the Japanese Prime Minister is coming out to proclaim that his country's financial situation is worse than Greece's, which has been a laughing stock of Europe for the better part of three decades. Japan is a very proud nation, and the fact that its Prime Minister made a statement like this should not be underappreciated.
As we noted last week, the 10-year and 30-year U.S. Treasury bonds are drifting higher as well. Earlier today, the 30-year bond yield surpassed 5%, which has been a psychological level that many have been pointed to as a critical tipping point. When you take a step back and look around the world it seems pretty clear that bond markets are sending a very strong signal. And that signal is that something is not well in the back end of the financial system.
This is even made clear when you look at the private sector, particularly at consumer debt. In late March, we warned of the growing trend of buy now, pay later schemes drifting down market as major credit card companies released charge-off data which showed charge-off rates reaching levels not seen since the 2008 great financial crisis. At the time, we could only surmise that Klarna was experiencing similar charge-off rates on the bigger-ticket items they financed and started doing deals with companies like DoorDash to finance burrito deliveries in an attempt to move down market to finance smaller ticket items with a higher potential of getting paid back. It seems like that inclination was correct as Klarna released data earlier today showing more losses on their book as consumers find it extremely hard to pay back their debts.

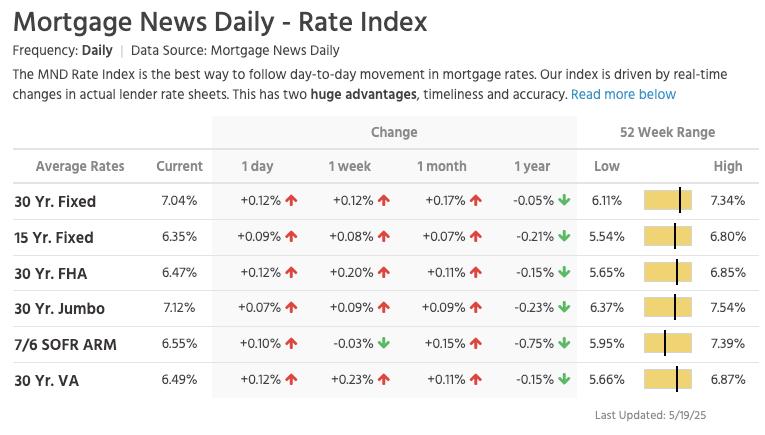
via NewsWire
This news hit the markets on the same day as the average rate of the 30-year mortgage in the United States rose to 7.04%. I'm not sure if you've checked lately, but real estate prices are still relatively elevated outside of a few big cities who expanded supply significantly during the COVID era as people flooded out of blue states towards red states. It's hard to imagine that many people can afford a house based off of sticker price alone, but with a 7% 30-year mortgage rate it's becoming clear that the ability of the Common Man to buy a house is simply becoming impossible.
via Lance Lambert
The mortgage rate data is not the only thing you need to look at to understand that it's becoming impossible for the Common Man of working age to buy a house. New data has recently been released that highlights That the median home buyer in 2007 was born in 1968, and the median home buyer in 2024 was born in 1968. Truly wild when you think of it. As our friend Darth Powell cheekily highlights below, we find ourselves in a situation where boomers are simply trading houses and the younger generations are becoming indentured slaves. Forever destined to rent because of the complete inability to afford to buy a house.
via Darth Powell
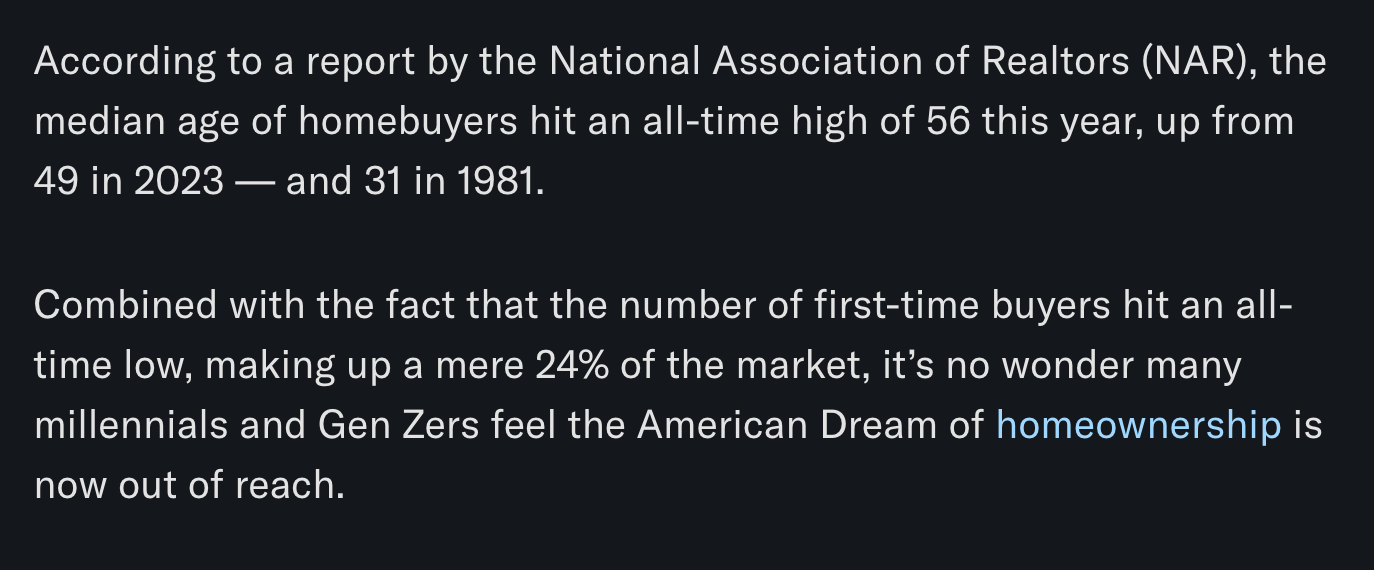
via Yahoo Finance
Meanwhile, Bitcoin re-approached all-time highs late this evening and looks primed for another breakout to the upside. This makes sense if you're paying attention. The high-velocity trash economy running on an obscene amount of debt in both the public and private sectors seems to be breaking at the seams. All the alarm bells are signaling that another big print is coming. And if you hope to preserve your purchasing power or, ideally, increase it as the big print approaches, the only thing that makes sense is to funnel your money into the hardest asset in the world, which is Bitcoin.

via Bitbo
Buckle up, freaks. It's gonna be a bumpy ride. Stay humble, Stack Sats.
Trump's Middle East Peace Strategy: Redefining U.S. Foreign Policy
In his recent Middle East tour, President Trump signaled what our guest Dr. Anas Alhajji calls "a major change in US policy." Trump explicitly rejected the nation-building strategies of his predecessors, contrasting the devastation in Afghanistan and Iraq with the prosperity of countries like Saudi Arabia and UAE. This marks a profound shift from both Republican and Democratic foreign policy orthodoxy. As Alhajji noted, Trump's willingness to meet with Syrian President Assad follows a historical pattern where former adversaries eventually become diplomatic partners.
"This is really one of the most important shifts in US foreign policy to say, look, sorry, we destroyed those countries because we tried to rebuild them and it was a big mistake." - Dr. Anas Alhajji
The administration's new approach emphasizes negotiation over intervention. Rather than military solutions, Trump is engaging with groups previously considered off-limits, including the Houthis, Hamas, and Iran. This pragmatic stance prioritizes economic cooperation and regional stability over ideological confrontation. The focus on trade deals and investment rather than regime change represents a fundamental reimagining of America's role in the Middle East.
Check out the full podcast here for more on the Iran nuclear situation, energy market predictions, and why AI development could create power grid challenges. Only on TFTC Studio.
Headlines of the Day
Bitcoin Soars to 100,217 sats | $106.00K While Bonds Lose 40% Since 2020 - via X
US Senate Advances Stablecoin Bill As America Embraces Bitcoin - via X
Get our new STACK SATS hat - via tftcmerch.io
Texas House Debates Bill For State-Run Bitcoin Reserve - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed 158,469 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
Don't let the noise consume you. Focus on making your life 1% better every day.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ b7274d28:c99628cb
2025-05-24 01:02:32
@ b7274d28:c99628cb
2025-05-24 01:02:32A few months ago, a nostrich was switching from iOS to Android and asked for suggestions for #Nostr apps to try out. nostr:npub18ams6ewn5aj2n3wt2qawzglx9mr4nzksxhvrdc4gzrecw7n5tvjqctp424 offered the following as his response:
nostr:nevent1qvzqqqqqqypzq0mhp4ja8fmy48zuk5p6uy37vtk8tx9dqdwcxm32sy8nsaa8gkeyqydhwumn8ghj7un9d3shjtnwdaehgunsd3jkyuewvdhk6tcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszythwden5te0dehhxarj9emkjmn99uqzpwwts6n28eyvjpcwvu5akkwu85eg92dpvgw7cgmpe4czdadqvnv984rl0z
Yes. #Android users are fortunate to have some powerful Nostr apps and tools at our disposal that simply have no comparison over on the iOS side. However, a tool is only as good as the knowledge of the user, who must have an understanding of how best to wield it for maximum effect. This fact was immediately evidenced by replies to Derek asking, "What is the use case for Citrine?" and "This is the first time I'm hearing about Citrine and Pokey. Can you give me links for those?"
Well, consider this tutorial your Nostr starter-kit for Android. We'll go over installing and setting up Amber, Amethyst, Citrine, and Pokey, and as a bonus we'll be throwing in the Zapstore and Coinos to boot. We will assume no previous experience with any of the above, so if you already know all about one or more of these apps, you can feel free to skip that tutorial.
So many apps...
You may be wondering, "Why do I need so many apps to use Nostr?" That's perfectly valid, and the honest answer is, you don't. You can absolutely just install a Nostr client from the Play Store, have it generate your Nostr identity for you, and stick with the default relays already set up in that app. You don't even need to connect a wallet, if you don't want to. However, you won't experience all that Nostr has to offer if that is as far as you go, any more than you would experience all that Italian cuisine has to offer if you only ever try spaghetti.
Nostr is not just one app that does one thing, like Facebook, Twitter, or TikTok. It is an entire ecosystem of applications that are all built on top of a protocol that allows them to be interoperable. This set of tools will help you make the most out of that interoperability, which you will never get from any of the big-tech social platforms. It will provide a solid foundation for you to build upon as you explore more and more of what Nostr has to offer.
So what do these apps do?

Fundamental to everything you do on Nostr is the need to cryptographically sign with your private key. If you aren't sure what that means, just imagine that you had to enter your password every time you hit the "like" button on Facebook, or every time you commented on the latest dank meme. That would get old really fast, right? That's effectively what Nostr requires, but on steroids.
To keep this from being something you manually have to do every 5 seconds when you post a note, react to someone else's note, or add a comment, Nostr apps can store your private key and use it to sign behind the scenes for you. This is very convenient, but it means you are trusting that app to not do anything with your private key that you don't want it to. You are also trusting it to not leak your private key, because anyone who gets their hands on it will be able to post as you, see your private messages, and effectively be you on Nostr. The more apps you give your private key to, the greater your risk that it will eventually be compromised.
Enter #Amber, an application that will store your private key in only one app, and all other compatible Nostr apps can communicate with it to request a signature, without giving any of those other apps access to your private key.
Most Nostr apps for Android now support logging in and signing with Amber, and you can even use it to log into apps on other devices, such as some of the web apps you use on your PC. It's an incredible tool given to us by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, and only available for Android users. Those on iPhone are incredibly jealous that they don't have anything comparable, yet.

Speaking of nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, the next app is also one of his making.
All Nostr data is stored on relays, which are very simple servers that Nostr apps read notes from and write notes to. In most forms of social media, it can be a pain to get your own data out to keep a backup. That's not the case on Nostr. Anyone can run their own relay, either for the sake of backing up their personal notes, or for others to post their notes to, as well.
Since Nostr notes take up very little space, you can actually run a relay on your phone. I have been on Nostr for almost 2 and a half years, and I have 25,000+ notes of various kinds on my relay, and a backup of that full database is just 24MB on my phone's storage.
Having that backup can save your bacon if you try out a new Nostr client and it doesn't find your existing follow list for some reason, so it writes a new one and you suddenly lose all of the people you were following. Just pop into your #Citrine relay, confirm it still has your correct follow list or import it from a recent backup, then have Citrine restore it. Done.
Additionally, there are things you may want to only save to a relay you control, such as draft messages that you aren't ready to post publicly, or eCash tokens, which can actually be saved to Nostr relays now. Citrine can also be used with Amber for signing into certain Nostr applications that use a relay to communicate with Amber.
If you are really adventurous, you can also expose Citrine over Tor to be used as an outbox relay, or used for peer-to-peer private messaging, but that is far more involved than the scope of this tutorial series.

You can't get far in Nostr without a solid and reliable client to interact with. #Amethyst is the client we will be using for this tutorial because there simply isn't another Android client that comes close, so far. Moreover, it can be a great client for new users to get started on, and yet it has a ton of features for power-users to take advantage of as well.
There are plenty of other good clients to check out over time, such as Coracle, YakiHonne, Voyage, Olas, Flotilla and others, but I keep coming back to Amethyst, and by the time you finish this tutorial, I think you'll see why. nostr:npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z and others who have contributed to Amethyst have really built something special in this client, and it just keeps improving with every update that's shipped.

Most social media apps have some form of push notifications, and some Nostr apps do, too. Where the issue comes in is that Nostr apps are all interoperable. If you have more than one application, you're going to have both of them notifying you. Nostr users are known for having five or more Nostr apps that they use regularly. If all of them had notifications turned on, it would be a nightmare. So maybe you limit it to only one of your Nostr apps having notifications turned on, but then you are pretty well locked-in to opening that particular app when you tap on the notification.
Pokey, by nostr:npub1v3tgrwwsv7c6xckyhm5dmluc05jxd4yeqhpxew87chn0kua0tjzqc6yvjh, solves this issue, allowing you to turn notifications off for all of your Nostr apps, and have Pokey handle them all for you. Then, when you tap on a Pokey notification, you can choose which Nostr app to open it in.
Pokey also gives you control over the types of things you want to be notified about. Maybe you don't care about reactions, and you just want to know about zaps, comments, and direct messages. Pokey has you covered. It even supports multiple accounts, so you can get notifications for all the npubs you control.

One of the most unique and incredibly fun aspects of Nostr is the ability to send and receive #zaps. Instead of merely giving someone a 👍️ when you like something they said, you can actually send them real value in the form of sats, small portions of a Bitcoin. There is nothing quite like the experience of receiving your first zap and realizing that someone valued what you said enough to send you a small amount (and sometimes not so small) of #Bitcoin, the best money mankind has ever known.
To be able to have that experience, though, you are going to need a wallet that can send and receive zaps, and preferably one that is easy to connect to Nostr applications. My current preference for that is Alby Hub, but not everyone wants to deal with all that comes along with running a #Lightning node. That being the case, I have opted to use nostr:npub1h2qfjpnxau9k7ja9qkf50043xfpfy8j5v60xsqryef64y44puwnq28w8ch for this tutorial, because they offer one of the easiest wallets to set up, and it connects to most Nostr apps by just copy/pasting a connection string from the settings in the wallet into the settings in your Nostr app of choice.
Additionally, even though #Coinos is a custodial wallet, you can have it automatically transfer any #sats over a specified threshold to a separate wallet, allowing you to mitigate the custodial risk without needing to keep an eye on your balance and make the transfer manually.

Most of us on Android are used to getting all of our mobile apps from one souce: the Google Play Store. That's not possible for this tutorial series. Only one of the apps mentioned above is available in Google's permissioned playground. However, on Android we have the advantage of being able to install whatever we want on our device, just by popping into our settings and flipping a toggle. Indeed, thumbing our noses at big-tech is at the heart of the Nostr ethos, so why would we make ourselves beholden to Google for installing Nostr apps?
The nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8 is an alternative app store made by nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9 as a resource for all sorts of open-source apps, but especially Nostr apps. What is more, you can log in with Amber, connect a wallet like Coinos, and support the developers of your favorite Nostr apps directly within the #Zapstore by zapping their app releases.
One of the biggest features of the Zapstore is the fact that developers can cryptographically sign their app releases using their Nostr keys, so you know that the app you are downloading is the one they actually released and hasn't been altered in any way. The Zapstore will warn you and won't let you install the app if the signature is invalid.
Getting Started
Since the Zapstore will be the source we use for installing most of the other apps mentioned, we will start with installing the Zapstore.
We will then use the Zapstore to install Amber and set it up with our Nostr account, either by creating a new private key, or by importing one we already have. We'll also use it to log into the Zapstore.
Next, we will install Amethyst from the Zapstore and log into it via Amber.
After this, we will install Citrine from the Zapstore and add it as a local relay on Amethyst.
Because we want to be able to send and receive zaps, we will set up a wallet with CoinOS and connect it to Amethyst and the Zapstore using Nostr Wallet Connect.
Finally, we will install Pokey using the Zapstore, log into it using Amber, and set up the notifications we want to receive.
By the time you are done with this series, you will have a great head-start on your Nostr journey compared to muddling through it all on your own. Moreover, you will have developed a familiarity with how things generally work on Nostr that can be applied to other apps you try out in the future.
Continue to Part 2: Installing the Zapstore. (Coming Soon)
-
 @ 3f770d65:7a745b24
2025-05-19 18:09:52
@ 3f770d65:7a745b24
2025-05-19 18:09:52🏌️ Monday, May 26 – Bitcoin Golf Championship & Kickoff Party
Location: Las Vegas, Nevada\ Event: 2nd Annual Bitcoin Golf Championship & Kick Off Party"\ Where: Bali Hai Golf Clubhouse, 5160 S Las Vegas Blvd, Las Vegas, NV 89119\ 🎟️ Get Tickets!
Details:
-
The week tees off in style with the Bitcoin Golf Championship. Swing clubs by day and swing to music by night.
-
Live performances from Nostr-powered acts courtesy of Tunestr, including Ainsley Costello and others.
-
Stop by the Purple Pill Booth hosted by Derek and Tanja, who will be on-boarding golfers and attendees to the decentralized social future with Nostr.
💬 May 27–29 – Bitcoin 2025 Conference at the Las Vegas Convention Center
Location: The Venetian Resort\ Main Attraction for Nostr Fans: The Nostr Lounge\ When: All day, Tuesday through Thursday\ Where: Right outside the Open Source Stage\ 🎟️ Get Tickets!
Come chill at the Nostr Lounge, your home base for all things decentralized social. With seating for \~50, comfy couches, high-tops, and good vibes, it’s the perfect space to meet developers, community leaders, and curious newcomers building the future of censorship-resistant communication.
Bonus: Right across the aisle, you’ll find Shopstr, a decentralized marketplace app built on Nostr. Stop by their booth to explore how peer-to-peer commerce works in a truly open ecosystem.
Daily Highlights at the Lounge:
-
☕️ Hang out casually or sit down for a deeper conversation about the Nostr protocol
-
🔧 1:1 demos from app teams
-
🛍️ Merch available onsite
-
🧠 Impromptu lightning talks
-
🎤 Scheduled Meetups (details below)
🎯 Nostr Lounge Meetups
Wednesday, May 28 @ 1:00 PM
- Damus Meetup: Come meet the team behind Damus, the OG Nostr app for iOS that helped kickstart the social revolution. They'll also be showcasing their new cross-platform app, Notedeck, designed for a more unified Nostr experience across devices. Grab some merch, get a demo, and connect directly with the developers.
Thursday, May 29 @ 1:00 PM
- Primal Meetup: Dive into Primal, the slickest Nostr experience available on web, Android, and iOS. With a built-in wallet, zapping your favorite creators and friends has never been easier. The team will be on-site for hands-on demos, Q\&A, merch giveaways, and deeper discussions on building the social layer of Bitcoin.
🎙️ Nostr Talks at Bitcoin 2025
If you want to hear from the minds building decentralized social, make sure you attend these two official conference sessions:
1. FROSTR Workshop: Multisig Nostr Signing
-
🕚 Time: 11:30 AM – 12:00 PM
-
📅 Date: Wednesday, May 28
-
📍 Location: Developer Zone
-
🎤 Speaker: nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgdwaehxw309ahx7uewd3hkcqpqs9etjgzjglwlaxdhsveq0qksxyh6xpdpn8ajh69ruetrug957r3qf4ggfm (Austin Kelsay) @ Voltage\ A deep-dive into FROST-based multisig key management for Nostr. Geared toward devs and power users interested in key security.
2. Panel: Decentralizing Social Media
-
🕑 Time: 2:00 PM – 2:30 PM
-
📅 Date: Thursday, May 29
-
📍 Location: Genesis Stage
-
🎙️ Moderator: nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqy08wumn8ghj7mn0wd68yttjv4kxz7fwv3jhyettwfhhxuewd4jsqgxnqajr23msx5malhhcz8paa2t0r70gfjpyncsqx56ztyj2nyyvlq00heps - Bitcoin Strategy @ Roxom TV
-
👥 Speakers:
-
nostr:nprofile1qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcppemhxue69uhkummn9ekx7mp0qqsy2ga7trfetvd3j65m3jptqw9k39wtq2mg85xz2w542p5dhg06e5qmhlpep – Early Bitcoin dev, CEO @ Sirius Business Ltd
-
nostr:nprofile1qy2hwumn8ghj7mn0wd68ytndv9kxjm3wdahxcqg5waehxw309ahx7um5wfekzarkvyhxuet5qqsw4v882mfjhq9u63j08kzyhqzqxqc8tgf740p4nxnk9jdv02u37ncdhu7e3 – Analyst & Partner @ Ego Death Capital
Get the big-picture perspective on why decentralized social matters and how Nostr fits into the future of digital communication.
🌃 NOS VEGAS Meetup & Afterparty
Date: Wednesday, May 28\ Time: 7:00 PM – 1:00 AM\ Location: We All Scream Nightclub, 517 Fremont St., Las Vegas, NV 89101\ 🎟️ Get Tickets!
What to Expect:
-
🎶 Live Music Stage – Featuring Ainsley Costello, Sara Jade, Able James, Martin Groom, Bobby Shell, Jessie Lark, and other V4V artists
-
🪩 DJ Party Deck – With sets by nostr:nprofile1qy0hwumn8ghj7cmgdae82uewd45kketyd9kxwetj9e3k7mf6xs6rgqgcwaehxw309ahx7um5wgh85mm694ek2unk9ehhyecqyq7hpmq75krx2zsywntgtpz5yzwjyg2c7sreardcqmcp0m67xrnkwylzzk4 , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgkwaehxw309anx2etywvhxummnw3ezucnpdejqqg967faye3x6fxgnul77ej23l5aew8yj0x2e4a3tq2mkrgzrcvecfsk8xlu3 , and more DJs throwing down
-
🛰️ Live-streamed via Tunestr
-
🧠 Nostr Education – Talks by nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq37amnwvaz7tmwdaehgu3dwfjkccte9ejx2un9ddex7umn9ekk2tcqyqlhwrt96wnkf2w9edgr4cfruchvwkv26q6asdhz4qg08pm6w3djg3c8m4j , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqg7waehxw309anx2etywvhxummnw3ezucnpdejz7ur0wp6kcctjqqspywh6ulgc0w3k6mwum97m7jkvtxh0lcjr77p9jtlc7f0d27wlxpslwvhau , nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq3vamnwvaz7tmwdaehgu3wd33xgetk9en82m30qqsgqke57uygxl0m8elstq26c4mq2erz3dvdtgxwswwvhdh0xcs04sc4u9p7d , nostr:nprofile1q9z8wumn8ghj7erzx3jkvmmzw4eny6tvw368wdt8da4kxamrdvek76mrwg6rwdngw94k67t3v36k77tev3kx7vn2xa5kjem9dp4hjepwd3hkxctvqyg8wumn8ghj7mn0wd68ytnhd9hx2qpqyaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgssuy4zk , nostr:nprofile1qy28wue69uhnzvpwxqhrqt33xgmn5dfsx5cqz9thwden5te0v4jx2m3wdehhxarj9ekxzmnyqqswavgevxe9gs43vwylumr7h656mu9vxmw4j6qkafc3nefphzpph8ssvcgf8 , and more.
-
🧾 Vendors & Project Booths – Explore new tools and services
-
🔐 Onboarding Stations – Learn how to use Nostr hands-on
-
🐦 Nostrich Flocking – Meet your favorite nyms IRL
-
🍸 Three Full Bars – Two floors of socializing overlooking vibrant Fremont Street
| | | | | ----------- | -------------------- | ------------------- | | Time | Name | Topic | | 7:30-7:50 | Derek | Nostr for Beginners | | 8:00-8:20 | Mark & Paul | Primal | | 8:30-8:50 | Terry | Damus | | 9:00-9:20 | OpenMike and Ainsley | V4V | | 09:30-09:50 | The Space | Space |
This is the after-party of the year for those who love freedom technology and decentralized social community. Don’t miss it.
Final Thoughts
Whether you're there to learn, network, party, or build, Bitcoin 2025 in Las Vegas has a packed week of Nostr-friendly programming. Be sure to catch all the events, visit the Nostr Lounge, and experience the growing decentralized social revolution.
🟣 Find us. Flock with us. Purple pill someone.
-
-
 @ 90152b7f:04e57401
2025-05-23 23:38:49
@ 90152b7f:04e57401
2025-05-23 23:38:49WikiLeaks The Global Intelligence Files
Released on 2013-03-04 00:00 GMT
| Email-ID | 296467 | | -------- | -------------------------- | | Date | 2007-10-29 20:54:22 | | From | <hrwpress@hrw.org> | | To | <responses@stratfor.com> |
Gaza: Israel's Fuel and Power Cuts Violate Laws of War\ \ For Immediate Release\ \ Gaza: Israel's Fuel and Power Cuts Violate Laws of War\ \ Civilians Should Not Be Penalized for Rocket Attacks by Armed Groups\ \ (New York, October 29, 2007) - Israel's decision to limit fuel and\ electricity to the Gaza Strip in retaliation for unlawful rocket attacks\ by armed groups amounts to collective punishment against the civilian\ population of Gaza, in violation of international law, and will worsen the\ humanitarian crisis there, Human Rights Watch said today.\ \ "Israel may respond to rocket attacks by armed groups to protect its\ population, but only in lawful ways," said Sarah Leah Whitson, director of\ Human Rights Watch's Middle East division. "Because Israel remains an\ occupying power, in light of its continuing restrictions on Gaza, Israel\ must not take measures that harm the civilian population - yet that is\ precisely what cutting fuel or electricity for even short periods will\ do."\ \ On Sunday, the Israeli Defense Ministry ordered the reduction of fuel\ shipments from Israel to Gaza. A government spokesman said the plan was to\ cut the amount of fuel by 5 to 11 percent without affecting the supply of\ industrial fuel for Gaza's only power plant.\ \ According to Palestinian officials, fuel shipments into Gaza yesterday\ fell by more than 30 percent.\ \ In response to the government's decision, a group of 10 Palestinian and\ Israeli human rights groups petitioned the Israeli Supreme Court on\ Sunday, seeking an immediate injunction against the fuel and electricity\ cuts. The court gave the government five days to respond but did not issue\ a temporary injunction. On Monday, the groups requested an urgent hearing\ before the five days expire.\ \ Last Thursday, Defense Minister Ehud Barak approved cutting electricity to\ Gaza for increasing periods in response to ongoing rocket attacks against\ civilian areas in Israel, but the government has not yet implemented the\ order.\ \ The rockets fired by Palestinian armed groups violate the international\ legal prohibition on indiscriminate attacks because they are highly\ inaccurate and cannot be directed at a specific target. Because Hamas\ exercises power inside Gaza, it is responsible for stopping indiscriminate\ attacks even when carried out by other groups, Human Rights Watch said.\ \ On Friday, Israeli Prime Minister Ehud Olmert said that Israel would\ respond strongly to the ongoing attacks without allowing a humanitarian\ crisis. But the UN's top humanitarian official, UN Deputy\ Secretary-General John Holmes, said that a "serious humanitarian crisis"\ in Gaza already exists, and called on Israel to lift the economic blockade\ that it tightened after Hamas seized power in June.\ \ Israel's decision to cut fuel and electricity is the latest move aimed\ ostensibly against Hamas that is affecting the entire population of Gaza.\ In September, the Israeli cabinet declared Gaza "hostile territory" and\ voted to "restrict the passage of various goods to the Gaza Strip and\ reduce the supply of fuel and electricity." Since then, Israel has\ increasingly blocked supplies into Gaza, letting in limited amounts of\ essential foodstuffs, medicine and humanitarian supplies. According to\ Holmes, the number of humanitarian convoys entering Gaza had dropped to\ 1,500 in September from 3,000 in July.\ \ "Cutting fuel and electricity obstructs vital services," Whitson said.\ "Operating rooms, sewage pumps, and water well pumps all need electricity\ to run."\ \ Israel sells to Gaza roughly 60 percent of the electricity consumed by the\ territory's 1.5 million inhabitants. In June 2006, six Israeli missiles\ struck Gaza's only power plant; today, for most residents, electricity is\ available during only limited hours.\ \ Israeli officials said they would cut electricity for 15 minutes after\ each rocket attack and then for increasingly longer periods if the attacks\ persist. Deputy Defense Minister Matan Vilnai said Israel would\ "dramatically reduce" the power it supplied to Gaza over a period of\ weeks.\ \ Cutting fuel or electricity to the civilian population violates a basic\ principle of international humanitarian law, or the laws of war, which\ prohibit a government that has effective control over a territory from\ attacking or withholding objects that are essential to the survival of the\ civilian population. Such an act would also violate Israel's duty as an\ occupying power to safeguard the health and welfare of the population\ under occupation.\ \ Israel withdrew its military forces and settlers from the Gaza Strip in\ 2005. Nonetheless, Israel remains responsible for ensuring the well-being\ of Gaza's population for as long as, and to the extent that, it retains\ effective control over the area. Israel still exercises control over\ Gaza's airspace, sea space and land borders, as well as its electricity,\ water, sewage and telecommunications networks and population registry.\ Israel can and has also reentered Gaza for security operations at will.\ \ Israeli officials state that by declaring Gaza "hostile territory," it is\ no longer obliged under international law to supply utilities to the\ civilian population, but that is a misstatement of the law.\ \ "A mere declaration does not change the facts on the ground that impose on\ Israel the status and obligations of an occupying power," said Whitson.\ \ For more information, please contact:\ \ In New York, Fred Abrahams (English, German): +1-917-385-7333 (mobile)\ \ In Washington, DC, Joe Stork (English): +1-202-299-4925 (mobile)\ \ In Cairo, Gasser Abdel-Razek (Arabic, English): +20-2-2-794-5036 (mobile);\ or +20-10-502-9999 (mobile)
-
 @ 34f1ddab:2ca0cf7c
2025-05-23 23:15:14
@ 34f1ddab:2ca0cf7c
2025-05-23 23:15:14Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ ecda4328:1278f072
2025-05-19 14:41:48
@ ecda4328:1278f072
2025-05-19 14:41:48An honest response to objections — and an answer to the most important question: why does any of this matter?
\ Statement: Deflation is not the enemy, but a natural state in an age of technological progress.\ Criticism: in real macroeconomics, long-term deflation is linked to depressions.\ Deflation discourages borrowers and investors, and makes debt heavier.\ Natural ≠ Safe.
1. “Deflation → Depression, Debt → Heavier”
This is true in a debt-based system. Yes, in a fiat economy, debt balloons to the sky, and without inflation it collapses.
But Bitcoin offers not “deflation for its own sake,” but an environment where you don’t need to be in debt to survive. Where savings don’t melt away.\ Jeff Booth said it clearly:
“Technology is inherently deflationary. Fighting deflation with the printing press is fighting progress.”
You don’t have to take on credit to live in this system. Which means — deflation is not an enemy, but an ally.
💡 People often confuse two concepts:
-
That deflation doesn’t work in an economy built on credit and leverage — that’s true.
-
That deflation itself is bad — that’s a myth.
📉 In reality, deflation is the natural state of a free market when technology makes everything cheaper.
Historical example:\ In the U.S., from the Civil War to the early 1900s, the economy experienced gentle deflation — alongside economic growth, employment expansion, and industrial boom.\ Prices fell: for example, a sack of flour cost \~$1.00 in 1865 and \~$0.50 in 1895 — and there was no crisis, because wages held and productivity increased.
Modern example:\ Consumer electronics over the past 20–30 years are a vivid example of technological deflation:\ – What cost $5,000 in 2000 (e.g., a 720p plasma TV) now costs $300 and delivers 10× better quality.\ – Phones, computers, cameras — all became far more powerful and cheaper at the same time.\ That’s how tech-driven deflation works: you get more for less.
📌 Bitcoin doesn’t make the world deflationary. It just doesn’t fight against deflation, unlike the fiat model that fights to preserve its debt pyramid.\ It stops punishing savers and rewards long-term thinkers.
Even economists often confuse organic tech deflation with crisis-driven (debt) deflation.
\ \ Statement: We’ve never lived in a truly free market — central banks and issuance always existed.\ Criticism: ideological statement.\ A truly “free” market is utopian.\ Banks and monetary issuance emerged in response to crises.\ A market without arbiters is not always fair, especially under imperfect competition.
2. “The Free Market Is a Utopia”
Yes, “pure markets” are rare. But what we have today isn’t regulation — it’s centralized power in the hands of central banks and cartels.
Bitcoin offers rules without rulers. 21 million. No one can change the issuance. It’s not ideology — it’s code instead of trust. And it has worked for 15 years.
\ \ Statement: Inflation is an invisible tax, especially on the poor and working class.\ Criticism: partly true: inflation can reduce debt burden, boost employment.\ The state indexes social benefits. Under stable inflation, compensators can work. Under deflation, things might be worse (mass layoffs, defaults).
3. “Inflation Can Help”
Theoretically — yes. Textbooks say moderate inflation can reduce debt burdens and stimulate consumption and jobs.\ But in practice — it works as a stealth tax, especially on those without assets. The wealthy escape — into real estate, stocks, funds.\ But the poor and working class lose purchasing power because their money is held in cash — and cash devalues.
💬 As Lyn Alden says:
“When your money can’t hold value, you’re forced to become an investor — even if you just want to save and live.”
The state may index pensions or benefits — but always with a lag, and always less than actual price increases.\ If bread rises 15% and your payment increase is 5%, you got poorer, even if the number on paper went up.
💥 We live in an inflationary system of everything:\ – Inflationary money\ – Inflationary products\ – Inflationary content\ – And now even inflationary minds
🧠 This is more than just rising prices — it’s a degradation of reality perception. You’re always rushing, everything loses meaning.\ But when did the system start working against you?
📉 What went wrong after 1971?
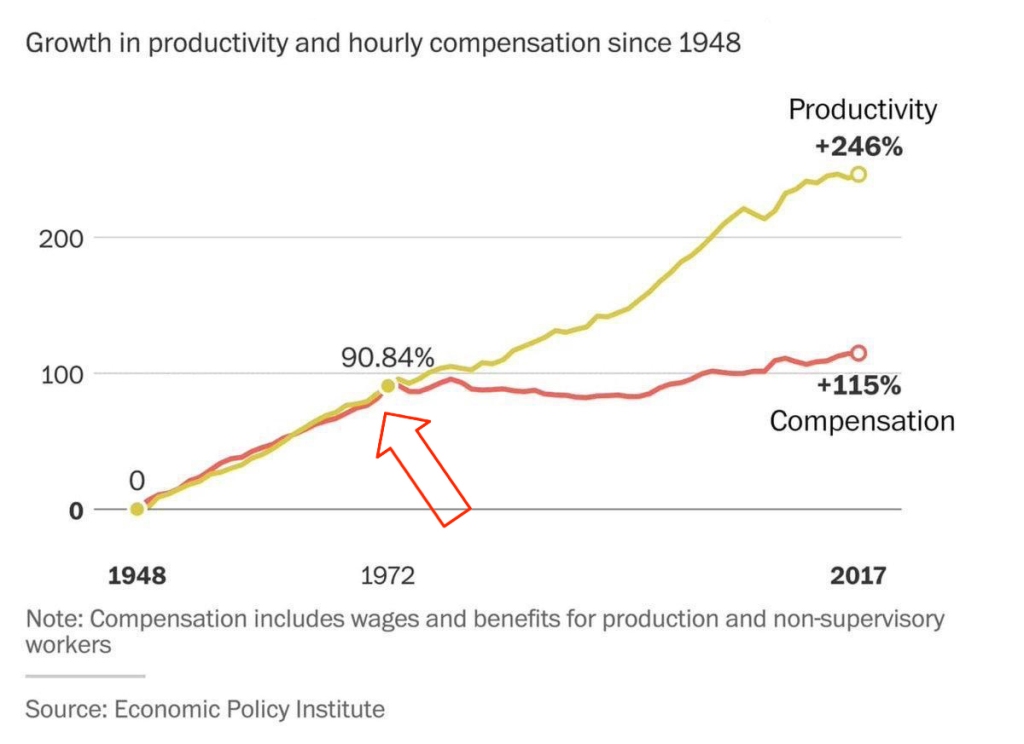 This chart shows that from 1948 to the early 1970s, productivity and wages grew together.\
But after the end of the gold standard in 1971 — the connection broke. Productivity kept rising, but real wages stalled.
This chart shows that from 1948 to the early 1970s, productivity and wages grew together.\
But after the end of the gold standard in 1971 — the connection broke. Productivity kept rising, but real wages stalled.👉 This means: you work more, better, faster — but buy less.
🔗 Source: wtfhappenedin1971.com
When you must spend today because tomorrow it’ll be worth less — that’s rewarding impulse and punishing long-term thinking.
Bitcoin offers a different environment:\ – Savings work\ – Long-term thinking is rewarded\ – The price of the future is calculated, not forced by a printing press
📌 Inflation can be a tool. But in government hands, it became a weapon — a slow, inevitable upward redistribution of wealth.
Indexing is weak compensation if bread is up 15% and your “increase” is only 5%.
\ \ Statement: War is not growth, but a reallocation of resources into destruction.
Criticism: war can spur technological leaps (Internet, GPS, nuclear energy — all from military programs). "Military Keynesianism" was a real model.
4. “War Drives R&D”
Yes, wars sometimes give rise to tech spin-offs: Internet, GPS, nuclear power — all originated from military programs.
But that doesn’t make war a source of progress — it makes tech a byproduct of catastrophe.
“War reallocates resources toward destruction — not growth.”
Progress doesn’t happen because of war — it happens despite it.
If scientific breakthroughs require a million dead and burnt cities — maybe you’ve built your economy wrong.
💬 Even Michael Saylor said:
“If you need war to develop technology — you’ve built civilization wrong.”
No innovation justifies diverting human labor, minds, and resources toward destruction.\ War is always the opposite of efficiency — more is wasted than created.
🧠 Bitcoin, on the other hand, is an example of how real R&D happens without violence.\ No taxes. No army. Just math, voluntary participation, and open-source code.
📌 Military Keynesianism is not a model of progress — it’s a symptom of a sick monetary system that needs destruction to reboot.
Bitcoin shows that coordination without violence is possible.\ This is R&D of a new kind: based not on destruction, but digital creation.
Statement: Bitcoin isn’t “Gold 1.0,” but an improved version: divisible, verifiable, unseizable.
Criticism: Bitcoin has no physical value; "unseizability" is a theory;\ Gold is material and autonomous.
5. “Bitcoin Has No Physical Value”
And gold does? Just because it shines?
Physical form is no guarantee of value.\ Real value lies in: scarcity, reliable transfer, verifiability, and non-confiscatability.
Gold is:\ – Hard to divide\ – Hard to verify\ – Expensive to store\ – Easy to seize
💡 Bitcoin is the first store of value in history that is fully free from physical limitations, and yet:\ – Absolutely scarce (21M, forever)\ – Instantly transferable over the Internet\ – Cryptographically verifiable\ – Controlled by no government
🔑 Bitcoin’s value lies in its liberation from the physical.\ It doesn’t need to be “backed” by gold or oil. It’s backed by energy, mathematics, and ongoing verification.
“Price is what you pay, value is what you get.” — Warren Buffett
When you buy bitcoin, you’re not paying for a “token” — you’re gaining access to a network of distributed financial energy.
⚡️ What are you really getting when you own bitcoin?\ – A key to a digital asset that can’t be faked\ – The ability to send “crystallized energy” anywhere on Earth\ – A role in a new accounting system that runs 24/7/365\ – Freedom: from banks, borders, inflation, and force
📉 Bitcoin doesn’t require physical value — because it creates value:\ Through trust, scarcity, and energy invested in mining.\ And unlike gold, it was never associated with slavery.
Statement: There’s no “income without risk” in Bitcoin: just hold — you preserve; want more — invest, risk, build.
Criticism: contradicts HODL logic; speculation remains dominant behavior.
6. “Speculation Dominates”
For now — yes. That’s normal for the early phase of a new technology. Awareness doesn’t come instantly.
What matters is not the motive of today’s buyer — but what they’re buying.
📉 A speculator may come and go — but the asset remains.\ And this asset is the only one in history that will never exist again. 21 million. Forever.
📌 Look deeper. Bitcoin has:\ – No CEO\ – No central issuer\ – No inflation\ – No “off switch”
💡 It’s not a stock. Not a startup. Not someone’s project.\ It’s a new foundation for trust.\ It’s opting out of a system where freedom is a privilege you’re granted under conditions.
🧠 People say: “Bitcoin can be copied.”\ Theoretically — yes.\ Practically — never.
Here’s what you’d need to recreate Bitcoin:\ – No pre-mine\ – A founder who disappears and never sells\ – No foundation or corporation\ – Tens of thousands of nodes worldwide\ – 701 million terahashes of hash power\ – Thousands of devs writing open protocols\ – Hundreds of global conferences\ – Millions of people defending digital sovereignty\ – All that without a single marketing budget
That’s all.
🔁 Everything else is an imitation, not a creation.\ Just like you can’t “reinvent fire” — Bitcoin can only exist once.
Statements:\ The Russia's '90s weren’t a free market — just anarchic chaos without rights protection.*\ Unlike fiat or even dollars, Bitcoin is the first asset with real defense — from governments, inflation, even thugs.\ And yes, even if your barber asks about Bitcoin — maybe it's not a bubble, but a sign that inflation has already hit everyone.
Criticism: Bitcoin’s protection isn’t universal — it works only with proper handling and isn’t available to all.\ Some just want to “get rich.”\ None of this matters because:
-
Bitcoin’s volatility (-30% in a week, +50% in a month) makes it unusable for price planning or contracts.
-
It can’t handle mass-scale usage.
-
To become currency, geopolitical will is needed — and without the first two, don’t even talk about the third.\ Also: “Bitcoin is too complicated for the average person.”
7. “It’s Too Complex for the Masses”
It’s complex — if you’re using L1 (Layer 1). But even grandmas use Telegram. In El Salvador, schoolkids buy lunch with Lightning. My barber installed Wallet of Satoshi in minutes right in front of me — and I now pay for my haircut via Lightning.
UX is just a matter of time. And it’s improving. Emerging tools:\ Cashu, Fedimint, Fedi, Wallet of Satoshi, Phoenix, Proton Wallet, Swiss Bitcoin Pay, Bolt Card / CoinCorner (NFC cards for Lightning payments).
This is like the internet in 1995:\ It started with modems — now it’s 4K streaming.
8. “Can’t Handle the Load”
A common myth.\ Yes, Bitcoin L1 processes about 7 transactions per second — intentionally. It’s not built to be Visa. It’s a financial protocol, just like TCP/IP is a network protocol. TCP/IP isn’t “fast” or “slow” — the experience depends on the infrastructure built on top: servers, routers, hardware. In the ’90s, it delivered text. Today, it streams Netflix. The protocol didn’t change — the stack did.
Same with Bitcoin: L1 defines rules, security, finality.\ Scaling and speed? That’s the second layer’s job.
To understand scale:
| Network | TPS (Transactions/sec) | | --- | --- | | Visa | up to 24,000 | | Mastercard | \~5,000 | | PayPal | \~193 | | Litecoin | \~56 | | Ethereum | \~20 | | Bitcoin | \~7 |
\ ⚡️ Enter Lightning Network — Bitcoin’s “fast lane.”\ It allows millions of transactions per second, instantly and nearly free.
And it’s not a sidechain.
❗️ Lightning is not a separate network.\ It uses real Bitcoin transactions (2-of-2 multisig). You can close the channel to L1 at any time. It’s not an alternative — it’s a native extension built into Bitcoin.\ Also evolving: Ark, Fedimint, eCash — new ways to scale and add privacy.
📉 So criticizing Bitcoin for “slowness” is like blaming TCP/IP because your old modem won’t stream YouTube.\ The protocol isn’t the problem — it’s the infrastructure.
🛡️ And by the way: Visa crashes more often than Bitcoin.
9. “We Need Geopolitical Will”
Not necessarily. All it takes is the will of the people — and leaders willing to act. El Salvador didn’t wait for G20 approval or IMF blessings. Since 2001, the country had used the US dollar as its official currency, abandoning its own colón. But that didn’t save it from inflation or dependency on foreign monetary policy. In 2021, El Salvador became the first country to recognize Bitcoin as legal tender. Since March 13, 2024, they’ve been purchasing 1 BTC daily, tracked through their public address:
🔗 Address\ 📅 First transaction
This policy became the foundation of their Strategic Bitcoin Reserve (SBR) — a state-led effort to accumulate Bitcoin as a national reserve asset for long-term stability and sovereignty.
Their example inspired others.
In March 2025, U.S. President Donald Trump signed an executive order creating the Strategic Bitcoin Reserve of the USA, to be funded through confiscated Bitcoin and digital assets.\ The idea: accumulate, don’t sell, and strategically expand the reserve — without extra burden on taxpayers.
Additionally, Senator Cynthia Lummis (Wyoming) proposed the BITCOIN Act, targeting the purchase of 1 million BTC over five years (\~5% of the total supply).\ The plan: fund it via revaluation of gold certificates and other budget-neutral strategies.
📚 More: Strategic Bitcoin Reserve — Wikipedia
👉 So no global consensus is required. No IMF greenlight.\ All it takes is conviction — and an understanding that the future of finance lies in decentralized, scarce assets like Bitcoin.
10. “-30% in a week, +50% in a month = not money”
True — Bitcoin is volatile. But that’s normal for new technologies and emerging money. It’s not a bug — it’s a price discovery phase. The world is still learning what this asset is.
📉 Volatility is the price of entry.\ 📈 But the reward is buying the future at a discount.
As Michael Saylor put it:
“A tourist sees Niagara Falls as chaos — roaring, foaming, spraying water.\ An engineer sees immense energy.\ It all depends on your mental model.”
Same with Bitcoin. Speculators see chaos. Investors see structural scarcity. Builders see a new financial foundation.
💡 Now consider gold:
👉 After the U.S. abandoned the gold standard in 1971, gold surged from \~$35 to over $800 in a decade — while suffering wild -40% to -60% crashes along the way.\ \ 📈 Gold Price Chart — Macrotrends\ \ Nobody said, “This can’t be money.” \ Because money is defined not by volatility, but by scarcity, adoption, and trust — which build over time.
📊 The more people save in Bitcoin, the more its volatility fades.
This is a journey — not a fixed state.
We don’t judge the internet by how it worked in 1994.\ So why expect Bitcoin to be the “perfect currency” in 2025?
It grows bottom-up — without regulators’ permission.\ And the longer it survives, the stronger it becomes.
Remember how many times it’s been declared dead.\ And how many times it came back — stronger.
📊 Gold vs. Bitcoin: Supply Comparison
This chart shows the key difference between the two hard assets:
🔹 Gold — supply keeps growing.\ Mining may be limited, but it’s still inflationary.\ Each year, there’s more — with no known cap: new mines, asteroid mining, recycling.
🔸 Bitcoin — capped at 21 million.\ The emission schedule is public, mathematically predictable, and ends completely around 2140.
🧠 Bottom line:\ Gold is good.\ Bitcoin is better — for predictability and scarcity.
💡 As Saifedean Ammous said:
“Gold was the best monetary good… until Bitcoin.”
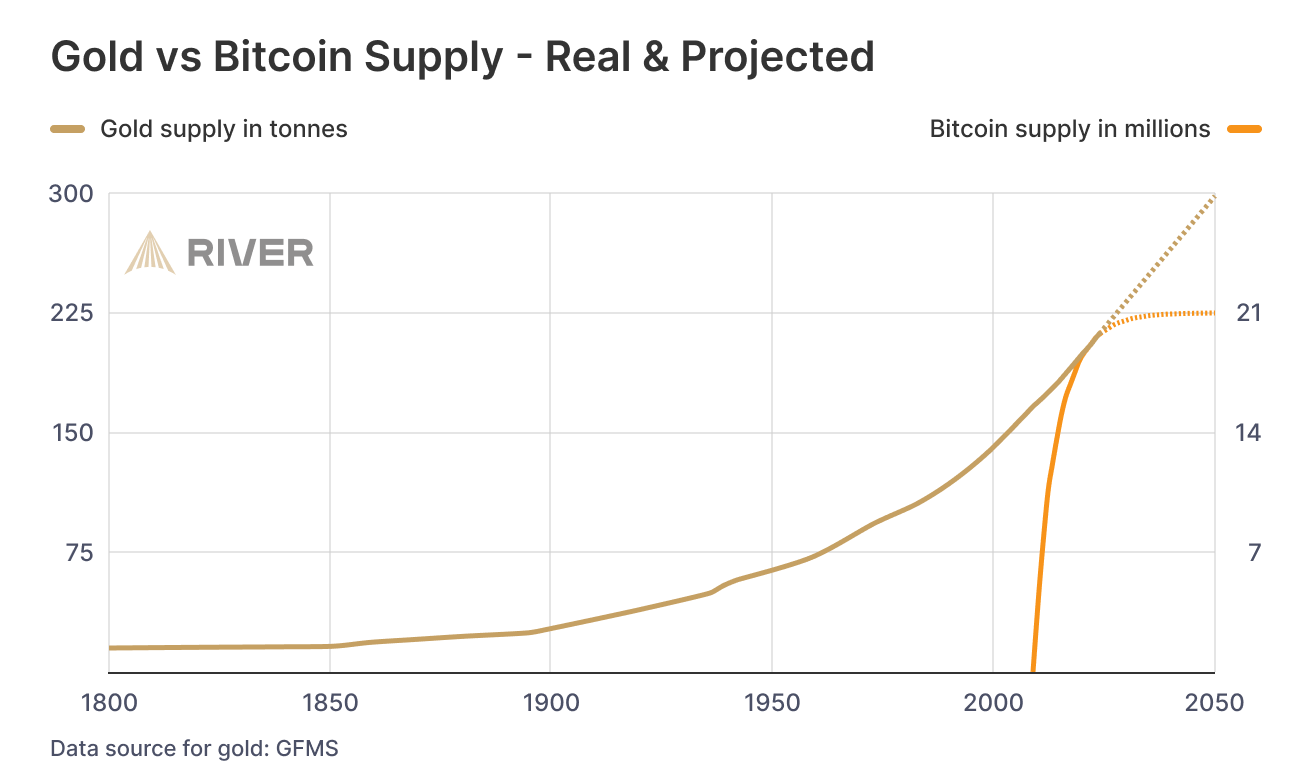
While we argue — fiat erodes every day.
No matter your view on Bitcoin, just show me one other asset that is simultaneously:
– immune to devaluation by decree\ – impossible to print more of\ – impossible to confiscate by a centralized order\ – impossible to counterfeit\ – and, most importantly — transferable across borders without asking permission from a bank, a state, or a passport
💸 Try sending $10,000 through PayPal from Iran to Paraguay, or Bangladesh to Saint Lucia.\ Good luck. PayPal doesn't even work there.
Now open a laptop, type 12 words — and you have access to your savings anywhere on Earth.
🌍 Bitcoin doesn't ask for permission.\ It works for everyone, everywhere, all the time.
📌 There has never been anything like this before.
Bitcoin is the first asset in history that combines:
– digital nature\ – predictable scarcity\ – absolute portability\ – and immunity from tyranny
💡 As Michael Saylor said:
“Bitcoin is the first money in human history not created by bankers or politicians — but by engineers.”
You can own it with no bank.\ No intermediary.\ No passport.\ No approval.
That’s why Bitcoin isn’t just “internet money” or “crypto” or “digital gold.”\ It may not be perfect — but it’s incorruptible.\ And it’s not going away.\ It’s already here.\ It is the foundation of a new financial reality.
🔒 This is not speculation. This is a peaceful financial revolution.\ 🪙 This is not a stock. It’s money — like the world has never seen.\ ⛓️ This is not a fad. It’s a freedom protocol.
And when even the barber starts asking about Bitcoin — it’s not a bubble.\ It’s a sign that the system is breaking.\ And people are looking for an exit.
For the first time — they have one.
💼 This is not about investing. It’s about the dignity of work.
Imagine a man who cleans toilets at an airport every day.
Not a “prestigious” job.\ But a crucial one.\ Without him — filth, bacteria, disease.
He shows up on time. He works with his hands.
And his money? It devalues. Every day.
He doesn’t work less — often he works more than those in suits.\ But he can afford less and less — because in this system, honest labor loses value each year.
Now imagine he’s paid in Bitcoin.
Not in some “volatile coin,” but in hard money — with a limited supply.\ Money that can’t be printed, reversed, or devalued by central banks.
💡 Then he could:
– Stop rushing to spend, knowing his labor won’t be worth less tomorrow\ – Save for a dream — without fear of inflation eating it away\ – Feel that his time and effort are respected — because they retain value
Bitcoin gives anyone — engineer or janitor — a way out of the game rigged against them.\ A chance to finally build a future where savings are real.
This is economic justice.\ This is digital dignity.
📉 In fiat, you have to spend — or your money melts.\ 📈 In Bitcoin, you choose when to spend — because it’s up to you.
🧠 In a deflationary economy, both saving and spending are healthy:
You don’t scramble to survive — you choose to create.
🎯 That’s true freedom.
When even someone cleaning floors can live without fear —\ and know that their time doesn’t vanish... it turns into value.
-
-
 @ 6c05c73e:c4356f17
2025-05-23 22:59:35
@ 6c05c73e:c4356f17
2025-05-23 22:59:35Como a grande maioria dos brasileiros. Eu não comecei um negócio porque “queria empreender”. Diferente disso, eu PRECISAVA para poder pagar contas e manter o básico.
Festas, openbar e camisas
Meu primeiro negócio foi na verdade um combo. Eu tinha saído do último trampo e eu gostava de festas. Então, comecei a organizar uma festa mensalmente na casa do meu pai. Eu pagava a água, energia e dava uma grana para ele. Em troca, organizava festa de sábado para domingo open bar.
A fórmula era simples. Criava o evento da festa no facebook, convidava todo mundo que conhecia. Panfletava na cidade e espalhava cartazes nos pontos de ônibus sobre a festa. E, para fechar com chave de ouro. Mulher era OFF até 20:00. Consequência? Os caras vinham e pagavam o ingresso deles e delas. Kkkkk. E, enchia…
Comecei a notar que a galera se vestia mal. E, pensei: "Porque não vestir eles?” Pimba! Comecei a desenha e confeccionar camisas para vender nas festas. E, pimba denovo! Vendeu, tudo! Fiz 2 coleções e mais algumas festas. Até o dia que um menino deu PT de tanto beber e decidi que era hora de tentar outra coisa.
Como assim a Apple não vai vender mais os carregadores?
Isso, foi durante a pandemia. A Apple decidiu vender o telefone e o cabo. E, você que lute com a fonte. Estava difícil achar dinheiro no mercado naqueles tempos e eu pensei. Vou pesquisar no google trends e validar a ideia. Caixa! Tinha mais de 80 pts de busca. Colei em SP, no Brás e comprei literalmente. Todo meu dinheiro de cabo de iphone, carregador e bateria portátil.
Fiquei com R$100 na conta. Para fazer um lanche e pagar pelo uber para voltar para casa. Chegando aqui, eu tirei foto e fiz várias copys. Anunciei no Olx, Mercado Livre e Facebook. Impulsionei os anúncios no OLX, vendi para familiares e amigos, e; vendia até para quem estava na rua. Fiz entrega de bike, a pé, de ônibus e é isso mesmo. Tem que ralar. Para queimar o resto da mercadoria. Deixei com uma loja de eletrônicos e fiz consignado. E, hora da próxima ideia.
Mulheres, doces e TPM
Meu penúltimo negócio veio depois dos cabos. Eu pesquisei na net, negócios online para começar com pouca grana. (Depois que paguei as contas do dia a dia, sobraram R$3mil). E, achei uma pesquisa mostrando que doces. Tinha baixa barreira de entrada e exigia poucos equipamentos. Eu trabalhei em restaurante por muitos anos e sabia como lucrar com aquilo. Além do mais, mulheres consomem mais doce em uma certa época do mês.
Não deu outra, convidei 2 pessoas para serem sócias. Desenvolvemos os produtos, fotografamos e fizemos as copys. Em sequência, precisávamos vender. Então, lá vamos denovo: Ifood, WPP, 99food (na época), Uber eats (na época), Elo7, famílias e amigos e; por fim começamos a vender consignado com alguns restaurantes e lojas. Foi uma época em que aprendi a prospectar clientes de todas as maneiras possíveis.
De novo, minha maior dificuldade era a locomoção para fazer entregas. Só tinha uma bike. Mas, entregávamos. Os primeiros 3 meses foram difíceis demais. Mas, rolou. No fim, nossas maiores vendas vinham de: Ifood, encomendas de festas e consignados. Mas, como nem tudo são flores. Meus dois sócios tomaram outros caminhos e abandonaram o projeto. Galera, está tudo bem com isso. Isso acontece o tempo todo. A vida muda e temos que aprender a aceitar isso. Vida que segue e fui para frente de novo.
Sobre paixões, paciência e acreditar
Estava eu comemorando meu níver de 30 anos, num misto de realizações e pouco realizado. Como assim? Sabe quando você faz um monte de coisas, mas ainda assim. Não sente que é aquilo? Pois então…
Eu amo investimentos, livros, escrever e sempre curti trocar ideia com amigos e família sobre como se desenvolver. Desde que comecei a usar a internet eu criei: Canal no youtube, páginas no IG e FB, pinterest, steemit, blog e até canal no Telegram. Mas, nunca tinha consistente sabe? Tipo assim, vou fazer isso por um ano e plantar 100 sementes aqui. Enfim, inconsistência te derruba meu amigo…Eu voltei a trabalhar com restaurantes e estava doido para mudar de área. Estava exausto de trabalhar e meu wpp não parava de tocar. Fui estudar ADM e Desenvolvimento de sistemas no Senac. Dois anos depois, formei. Consegui trabalho.
E, comecei a pensar em como criar um negócio online, escalável e multilíngue. Passei os próximos 7 meses desenhando e pensando como. Mas, tinha que dar o primeiro passo. Criei um site e fui escrevendo textos. Os primeiros 30 foram aquilo, os próximos 10 melhoraram muito e os 10 a seguir eu fiquei bem satisfeitos. Hoje, tenho o negócio que estava na cabeça desde 2023. Mas, olha o tamanho da volta que o universo me fez dar e aprender para chegar aqui hoje. Dicas? Só 3:
- Você precisa usar a internet para fazer negócio. Em todos os negócios que falei, sempre teve algo online. Não negligencie isso.
- Tem que aprender a vender e se vender.
- Confia em si mesmo e faz sem medo de errar. Porque, advinha? Você vai errar! Mas, vai aprender e melhorar. Tem que persistir…
Por hoje é isso. Tamo junto!
-
 @ bf47c19e:c3d2573b
2025-05-23 22:14:37
@ bf47c19e:c3d2573b
2025-05-23 22:14:37Originalni tekst na antenam.net
22.05.2025 / Autor: Ana Nives Radović
Da nema besplatnog ručka sigurno ste čuli svaki put kad bi neko poželio da naglasi da se sve na neki način plaća, iako možda tu cijenu ne primjećujemo odmah. Međutim, kada govorimo o događaju od kojeg je prošlo tačno 15 godina onda o „ručku“ ne govorimo u prenešenom smislu, već o porudžbini pice čija tržišna vrijednost iz godine u godinu dostiže iznos koji je čini najskupljom hranom koja je ikad poručena.
Tog 22. maja 2010. godine čovjek sa Floride pod imenom Laslo Hanjec potrošio je 10.000 bitcoina na dvije velike pice. U to vrijeme, ta količina bitcoina imala je tržišnu vrijednost od oko 41 dolar. Ako uzmemo u obzir da je vrijednost jedne jedinice ove digitalne valute danas nešto više od 111.000 dolara, tih 10.000 bitcoina danas bi značilo vrijednost od 1,11 milijardi dolara.
Nesvakidašnji događaj u digitalnoj i ugostiteljskoj istoriji, nastao zbog znatiželje poručioca koji je želio da se uvjeri da koristeći bitcoin može da plati nešto u stvarnom svijetu, pretvorio se u Bitcoin Pizza Day, kao podsjetnik na trenutak koji je označio prelaz bitcoina iz apstraktnog kriptografskog eksperimenta u nešto što ima stvarnu vrijednost.
Hanjec je bio znatiželjan i pitao se da li se prva, a u to vrijeme i jedina kriptovaluta može iskoristiti za kupovinu nečeg opipljivog. Objavio je ponudu na jednom forumu koja je glasila: 10.000 BTC za dvije pice. Jedan entuzijasta se javio, naručio pice iz restorana Papa John’s i ispisao zanimljivu stranicu istorije digitalne imovine.
Taj inicijalni zabilježeni finansijski dogovor dao je bitcoinu prvu široko prihvaćenu tržišnu vrijednost: 10.000 BTC za 41 dolar, čime je bitcoin napravio svoj prvi korak ka onome što danas mnogi zovu digitalnim zlatom.
Šta je zapravo bitcoin?
Bitcoin je oblik digitalnog novca koji je osmišljen da bude decentralizovan, transparentan i otporan na uticaj centralnih banaka. Kreirao ga je 2009. godine anonimni autor poznat kao Satoši Nakamoto, neposredno nakon globalne finansijske krize 2008. godine. U svojoj suštini, bitcoin je protokol, skup pravila koja sprovodi kompjuterski kod, koji omogućava korisnicima da bez posrednika sigurno razmjenjuju vrijednost putem interneta.
Osnova cijelog sistema je blockchain, distribuisana digitalna knjiga koju održavaju hiljade nezavisnih računara (tzv. čvorova) širom svijeta. Svaka transakcija se bilježi u novi „blok“, koji se potom dodaje u lanac (otud naziv „lanac blokova“, odnosno blockchain). Informacija koja se jednom upiše u blok ne može da se izbriše, niti promijeni, što omogućava više transparentnosti i više povjerenja.
Da bi blockchain mreža u kojoj se sve to odvija zadržala to svojstvo, bitcoin koristi mehanizam konsenzusa nazvan dokaz rada (proof-of-work), što znači da specijalizovani računari koji „rudare“ bitcoin rješavaju kompleksne matematičke probleme kako bi omogućili obavljanje transakcija i pouzdanost mreže.
Deflatorna priroda bitcoina
Najjednostavniji način da se razumije deflatorna priroda bitcoina je da pogledamo cijene izražene u valuti kojoj plaćamo. Sigurno ste u posljednje vrijeme uhvatili sebe da komentarišete da ono što je prije nekoliko godina koštalo 10 eura danas košta 15 ili više. Budući da to ne zapažate kada je u pitanju cijena samo određenog proizvoda ili usluge, već kao sveprisutan trend, shvatate da se radi o tome da je novac izgubio vrijednost. Na primjer, kada je riječ o euru, otkako je Evropska centralna banka počela intenzivno da doštampava novac svake godine, pa je od 2009. kada je program tzv. „kvantitativnog popuštanja“ započet euro zabilježio kumulativnu inflaciju od 42,09% zbog povećane količine sredstava u opticaju.
Međutim, kada je riječ o bitcoinu, njega nikada neće biti više od 21 milion koliko je izdato prvog dana, a to nepromjenjivo pravilo zapisano je i u njegovom kodu. Ova ograničena ponuda oštro se suprotstavlja principima koji važe kod monetarnih institucija, poput centralnih banaka, koje doštampavaju novac, često da bi povećale količinu u opticaju i tako podstakle finansijske tokove, iako novac zbog toga gubi vrijednost. Nasuprot tome, bitcoin se zadržava na iznosu od 21 milion, pa je upravo ta konačnost osnova za njegovu deflatornu prirodu i mogućnost da vremenom dobija na vrijednosti.
Naravno, ovo ne znači da je cijena bitcoina predodređena da samo raste. Ona je zapravo prilično volatilna i oscilacije su česte, posebno ukoliko, na primjer, posmatramo odnos cijena unutar jedne godine ili nekoliko mjeseci, međutim, gledano sa vremenske distance od četiri do pet godina bilo koji uporedni period od nastanka bitcoina do danas upućuje na to da je cijena u međuvremenu porasla. Taj trend će se nastaviti, tako da, kao ni kada je riječ o drugim sredstvima, poput zlata ili nafte, nema mjesta konstatacijama da je „vrijeme niskih cijena prošlo“.
Šta zapravo znači ovaj dan?
Bitcoin Pizza Day je za mnoge prilika da saznaju ponešto novo o bitcoinu, jer tada imaju priliku da o njemu čuju detalje sa raznih strana, jer kako se ovaj događaj popularizuje stvaraju se i nove prilike za učenje. Takođe, ovaj dan od 2021. obilježavaju picerije širom svijeta, u više od 400 gradova iz najmanje 75 zemalja, jer je za mnoge ovo prilika da korisnike bitcoina navedu da potroše djelić svoje imovine na nešto iz njihove ponude. Naravno, taj iznos je danasd zanemarljivo mali, a cijena jedne pice danas je otprilike 0,00021 bitcoina.
No, dok picerije širom svijeta danas na zabavan način pokušavaju da dođu do novih gostiju, ovaj dan je za mnoge vlasnike bitcoina nešto poput opomene da svoje digitalne novčiće ipak ne treba trošiti na nešto potrošno, jer je budućnost nepredvidiva. Bitcoin Pizza Day je dan kada se ideja pretvorila u valutu, kada su linije koda postale sredstvo razmjene.
Prvi let avionom trajao je svega 12 sekundi, a u poređenju sa današnjim transkontinentalnim linijama to djeluje gotovo neuporedivo i čudno, međutim, od nečega je moralo početi. Porudžbina pice plaćene bitcoinom označile su početak razmjene ove vrste, dok se, na primjer, tokom jučerašnjeg dana obim plaćanja bitcoinom premašio 23 milijarde dolara. Nauka i tehnologija nas podsjećaju na to da sve počinje malim, zanemarivim koracima.
-
 @ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03
@ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ b83a28b7:35919450
2025-05-16 19:23:58
@ b83a28b7:35919450
2025-05-16 19:23:58This article was originally part of the sermon of Plebchain Radio Episode 110 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ bf47c19e:c3d2573b
2025-05-23 21:54:43
@ bf47c19e:c3d2573b
2025-05-23 21:54:43Srpski prevod knjige "The Little Bitcoin Book"
Zašto je Bitkoin bitan za vašu slobodu, finansije i budućnost?
Verovatno ste čuli za Bitkoin u vestima ili da o njemu raspravljaju vaši prijatelji ili kolege. Kako to da se cena stalno menja? Da li je Bitkoin dobra investicija? Kako to uopšte ima vrednost? Zašto ljudi stalno govore o tome kao da će promeniti svet?
"Mala knjiga o Bitkoinu" govori o tome šta nije u redu sa današnjim novcem i zašto je Bitkoin izmišljen da obezbedi alternativu trenutnom sistemu. Jednostavnim rečima opisuje šta je Bitkoin, kako funkcioniše, zašto je vredan i kako utiče na individualnu slobodu i mogućnosti ljudi svuda - od Nigerije preko Filipina do Venecuele do Sjedinjenih Država. Ova knjiga takođe uključuje odeljak "Pitanja i odgovori" sa nekim od najčešće postavljanih pitanja o Bitkoinu.
Ako želite da saznate više o ovom novom obliku novca koji i dalje izaziva interesovanje i usvajanje širom sveta, onda je ova knjiga za vas.
-
 @ 611021ea:089a7d0f
2025-05-24 00:00:04
@ 611021ea:089a7d0f
2025-05-24 00:00:04The world of health and fitness data is booming. Users are tracking more aspects of their well-being than ever before, from daily steps and workout intensity to sleep patterns and caloric intake. But for developers looking to build innovative applications on this data, significant hurdles remain: ensuring user privacy, achieving interoperability between different services, and simply managing the complexity of diverse health metrics.
Enter the NIP-101h Health Profile Framework and its companion tools: the HealthNote SDK and the HealthNote API. This ecosystem is designed to empower developers to create next-generation health and fitness applications that are both powerful and privacy-preserving, built on the decentralized and user-centric principles of Nostr.
NIP-101h: A Standardized Language for Health Metrics
At the core of this ecosystem is NIP-101h. It's a Nostr Improvement Proposal that defines a standardized way to represent, store, and share granular health and fitness data. Instead of proprietary data silos, NIP-101h introduces specific Nostr event kinds for individual metrics like weight (kind
1351), height (kind1352), step count (kind1359), and many more.Key features of NIP-101h:
- Granularity: Each piece of health information (e.g., weight, caloric intake) is a distinct Nostr event, allowing for fine-grained control and access.
- User Control: Built on Nostr, the data remains under user control. Users decide what to share, with whom, and on which relays.
- Standardization: Defines common structures for units, timestamps, and metadata, promoting interoperability.
- Extensibility: New metrics can be added as new NIP-101h.X specifications, allowing the framework to evolve.
- Privacy by Design: Encourages the use of NIP-04/NIP-44 for encryption and includes a
consenttag for users to specify data-sharing preferences.
You can explore the full NIP-101h specification and its metric directory in the main project repository.
The HealthNote SDK: Simplifying Client-Side Integration
While NIP-101h provides the "what," the HealthNote SDK provides the "how" for client-side applications. This (currently draft) TypeScript SDK aims to make it trivial for developers to:
- Create & Validate NIP-101h Events: Easily construct well-formed Nostr events for any supported health metric, ensuring they conform to the NIP-101h specification.
- Handle Encryption: Seamlessly integrate with NIP-44 to encrypt sensitive health data before publication.
- Manage Consent: Automatically include appropriate
consenttags (e.g., defaulting toaggregate-only) to respect user preferences. - Publish to Relays: Interact with Nostr relays to publish the user's health data.
- Prepare Data for Analytics: Extract minimal, privacy-preserving "stat-blobs" for use with the HealthNote API.
The SDK's goal is to abstract away the low-level details of Nostr event creation and NIP-101h formatting, letting developers focus on their application's unique features.
The HealthNote API: Powerful Insights, Zero Raw Data Exposure
This is where things get really exciting for developers wanting to build data-driven features. The HealthNote API (detailed in
HealthNote-API.md) is a server-side component designed to provide powerful analytics over aggregated NIP-101h data without ever accessing or exposing individual users' raw, unencrypted metrics.Here's how it achieves this:
- Privacy-Preserving Ingestion: The SDK sends only "stat-blobs" to the API. These blobs contain the numeric value, unit, timestamp, and metric kind, but not the original encrypted content or sensitive user identifiers beyond what's necessary for aggregation.
- Aggregation at its Core: The API's endpoints are designed to return only aggregated data.
GET /trend: Provides time-series data (e.g., average daily step count over the last month).GET /correlate: Computes statistical correlations between two metrics (e.g., does increased activity duration correlate with changes in workout intensity?).GET /distribution: Shows how values for a metric are distributed across the user base.
- Built-in Privacy Techniques:
- k-Anonymity: Ensures that each data point in an aggregated response represents at least 'k' (e.g., 5) distinct users, preventing re-identification.
- Differential Privacy (Optional): Can add statistical noise to query results, further protecting individual data points while preserving overall trends.
- No Raw Data Access for Developers: Developers querying the API receive only these aggregated, anonymized results, perfect for powering charts, dashboards, and trend analysis in their applications.
A Typical Workflow
- A user records a workout in their NIP-101h-compatible fitness app.
- The app uses the HealthNote SDK to create NIP-101h events for metrics like distance, duration, and calories burned. Sensitive data is encrypted.
- The SDK publishes these events to the user's configured Nostr relays.
- The SDK also extracts stat-blobs (e.g.,
{ kind: 1363, value: 5, unit: 'km', ... }) and sends them to the HealthNote API for ingestion, tagged with anaggregate-onlyconsent. - Later, the app (or an authorized third-party service) queries the HealthNote API:
GET /trend?kind=1363&bucket=week&stat=sum. - The API returns a JSON object like:
{"series": [{"date": "2024-W20", "value": 15000}, ...]}showing the total distance run by all consenting users, week by week. This data can directly populate a trend chart.
Benefits for the Ecosystem
- For Users:
- Greater control and ownership of their health data.
- Ability to use a diverse range of interoperable health and fitness apps.
- Confidence that their data can contribute to insights without sacrificing personal privacy.
- For Developers:
- Easier to build sophisticated health and fitness applications without becoming privacy experts or building complex data aggregation pipelines.
- Access to rich, aggregated data for creating compelling user-facing features (trends, benchmarks, correlations).
- Reduced burden of storing and securing sensitive raw health data for analytical purposes.
- Opportunity to participate in an open, interoperable ecosystem.
The Road Ahead
The NIP-101h framework, the HealthNote SDK, and the HealthNote API are foundational pieces for a new generation of health and fitness applications. As these tools mature and gain adoption, we envision a vibrant ecosystem where users can seamlessly move their data between services, and developers can innovate rapidly, all while upholding the highest standards of privacy and user control.
We encourage developers to explore the NIP-101h specifications, experiment with the (upcoming) SDK, and review the HealthNote API design. Your feedback and contributions will be invaluable as we build this privacy-first future for health data.
https://github.com/HealthNoteLabs
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:53:16
@ 6d5c826a:4b27b659
2025-05-23 21:53:16- DefGuard - True enterprise WireGuard with MFA/2FA and SSO. (Source Code)
Apache-2.0Rust - Dockovpn - Out-of-the-box stateless dockerized OpenVPN server which starts in less than 2 seconds. (Source Code)
GPL-2.0Docker - Firezone - WireGuard based VPN Server and Firewall. (Source Code)
Apache-2.0Docker - Gluetun VPN client - VPN client in a thin Docker container for multiple VPN providers, written in Go, and using OpenVPN or Wireguard, DNS over TLS, with a few proxy servers built-in.
MITdocker - Headscale - Self-hostable fork of Tailscale, cross-platform clients, simple to use, built-in (currently experimental) monitoring tools.
BSD-3-ClauseGo - Nebula - A scalable p2p VPN with a focus on performance, simplicity and security.
MITGo - ocserv - Cisco AnyConnect-compatible VPN server. (Source Code)
GPL-2.0C - OpenVPN - Uses a custom security protocol that utilizes SSL/TLS for key exchange. (Source Code)
GPL-2.0C - SoftEther - Multi-protocol software VPN with advanced features. (Source Code)
Apache-2.0C - sshuttle - Poor man's VPN.
LGPL-2.1Python - strongSwan - Complete IPsec implementation for Linux. (Source Code)
GPL-2.0C - WireGuard - Very fast VPN based on elliptic curve and public key crypto. (Source Code)
GPL-2.0C
- DefGuard - True enterprise WireGuard with MFA/2FA and SSO. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:52:59
@ 6d5c826a:4b27b659
2025-05-23 21:52:59- Ganeti - Cluster virtual server management software tool built on top of KVM and Xen. (Source Code)
BSD-2-ClausePython/Haskell - KVM - Linux kernel virtualization infrastructure. (Source Code)
GPL-2.0/LGPL-2.0C - OpenNebula - Build and manage enterprise clouds for virtualized services, containerized applications and serverless computing. (Source Code)
Apache-2.0C++ - oVirt - Manages virtual machines, storage and virtual networks. (Source Code)
Apache-2.0Java - Packer - A tool for creating identical machine images for multiple platforms from a single source configuration. (Source Code)
MPL-2.0Go - Proxmox VE - Virtualization management solution. (Source Code)
GPL-2.0Perl/Shell - QEMU - QEMU is a generic machine emulator and virtualizer. (Source Code)
LGPL-2.1C - Vagrant - Tool for building complete development environments. (Source Code)
BUSL-1.1Ruby - VirtualBox - Virtualization product from Oracle Corporation. (Source Code)
GPL-3.0/CDDL-1.0C++ - XCP-ng - Virtualization platform based on Xen Source and Citrix® Hypervisor (formerly XenServer). (Source Code)
GPL-2.0C - Xen - Virtual machine monitor for 32/64 bit Intel / AMD (IA 64) and PowerPC 970 architectures. (Source Code)
GPL-2.0C
- Ganeti - Cluster virtual server management software tool built on top of KVM and Xen. (Source Code)
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:52:43
@ 6d5c826a:4b27b659
2025-05-23 21:52:43- Darcs - Cross-platform version control system, like git, mercurial or svn but with a very different approach: focus on changes rather than snapshots. (Source Code)
GPL-2.0Haskell - Fossil - Distributed version control with built-in wiki and bug tracking. (Source Code)
BSD-2-ClauseC - Git - Distributed revision control and source code management (SCM) with an emphasis on speed. (Source Code)
GPL-2.0C - Mercurial - Distributed source control management tool. (Source Code)
GPL-2.0Python/C/Rust - Subversion - Client-server revision control system. (Source Code)
Apache-2.0C
- Darcs - Cross-platform version control system, like git, mercurial or svn but with a very different approach: focus on changes rather than snapshots. (Source Code)
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 0b118e40:4edc09cb
2025-05-15 14:44:54
@ 0b118e40:4edc09cb
2025-05-15 14:44:54My week started off with a lovely message from a friend : “I often think about you. Especially during times when it requires me to be more resilient and have faith in myself. I always carry your note in the book you gave me, “what the dog saw” And it always gives me courage and I send a little prayer your way”.
This friend of mine was dealing with the undercurrent of discrimination in my alma mater when we first met, and I helped out. It's something anybody would have done, but surprisingly, nobody else showed up. We’ve stayed in touch over the years, and my friend went on to help a lot of other people along the way.
I don’t remember what I wrote in that note. It’s something I tend to do (write notes, give books, write notes in books). But the message boomeranged back to me at a time when I needed to hold the line. To keep the faith.
Most of us don’t talk about our struggles. And sometimes the smallest act, which could just be a kind word or a reminder of the person you are, can carry farther than we imagine.
On the act of giving
There’s a book called Give and Take by Adam Grant. I picked it up hoping to learn how to take, because it’s always been easier to give and harder to accept help. But what I learned was something else entirely.
Grant studied over 30,000 people across different companies and grouped them into three types: * Givers * Matchers * Takers
Based on his studies, givers often finish last... They struggle the most. They burn out. They get overlooked. They’re too trusting.
But oddly, they also rise to the very top.
Matchers are the scorekeepers, the “I’ll help you if you help me” kind. They make up most of the population. The fascinating thing about tit-for-tat is that if someone’s kind, they reciprocate. But if someone acts like a jerk, they return the energy, and over time, it becomes a pool of spoiled milk. Matchers are a lukewarm, forgettable kind of network.
Takers are the ones chasing attention, always aligning themselves with whoever looks powerful. They tend to float toward status and soak up what they can. But they often portray themselves as kind and giving.
One example Grant shared was Enron's Kenneth Lay, who was at the center of one of the biggest corporate scandals in U.S. history. He hung around wherever he’d get seen or validated. He funded both Bush and Clinton, hedging his bets on who might win by securing proximity. Sadly, when Enron crumbled, he died of a heart attack before his prison sentencing.
Most people steer clear from takers because they are just exhausting. And takers often collapse under the weight of their own games.
But takers aren’t the lowest performers. That spot belongs to a certain kind of giver—the self-neglecting kind. The ones with no boundaries, no clarity, and no self-awareness. They give in to avoid conflict, to feel worthy, or because they don’t know how to say no. And when life breaks them, they point fingers.
Then there’s the other kind of giver. The ones who build trust and build people up without asking for a receipt.
These givers: 1. Help without expecting anything in return 2. Don’t seek validation or recognition 3. Care more about effort, growth, and potential than titles or status 4. Build and connect to uplift others, not to be seen 5. Listen deeply, speak with intention, and influence through humility 6. Say yes only when their strengths genuinely add value 7. Give from a place of purpose, not insecurity or people-pleasing 8. Hold their ground. They don’t get walked over 9. Recognise takers early, and step back when giving becomes draining 10. Let their work speak. They lead with calm strength when it matters
This group of givers rarely talk much about what they do for others. But when you hear about it or see it, it stays with you. It makes you want to show up a little better.
Why open source environments feels like home
The more I thought about it, the more I saw how deeply open source reflects that kind of giving that ends up right at the top.
In open source, you don’t last if it’s just about ego. You can’t fake it. There are no titles, no awards. You either show up to build and help, or you don’t.
People who give without needing to be seen are the ones the community leans on. You can tell when someone’s pretending to care. It’s in their tone, their urgency and their sense of transaction. The genuine ones don’t need to brand themselves as generous. They just are.
Open source works because giving is the default setting. The work speaks volumes and generosity compounds. The system filters for people who show up with purpose and stay consistent.
It’s also why the ones who whine, posture, or manipulate rarely last. They might call themselves givers, but they’re not fooling anyone who’s actually doing the work.
Adam Grant found that for giver cultures to thrive, takers have to be removed. They need to be pruned. Because takers poison the well. They drain givers, shift the culture from contribution to calculation, and unravel the trust that holds open systems together.
When hope boomerangs
That note is something I don’t remember writing. But it found its way back to me, and it was a good reminder to take my own advice and keep the faith.
And maybe that’s the point.
You do a small thing. And years later, it circles back when it matters most. Not because you expected it. But because you mattered.
According to Grant, givers do best when they combine generosity with grit and strategy. They create networks built on goodwill, which eventually open doors others don’t even know exist.
So if you’re wondering where I’m going with this, do something genuinely kind for someone today. Even if it’s as simple as sending a kind note. Not for you to be seen or heard. And not for you to keep scores.
But, just because.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:52:26
@ 6d5c826a:4b27b659
2025-05-23 21:52:26- grml - Bootable Debian Live CD with powerful CLI tools. (Source Code)
GPL-3.0Shell - mitmproxy - A Python tool used for intercepting, viewing and modifying network traffic. Invaluable in troubleshooting certain problems. (Source Code)
MITPython - mtr - Network utility that combines traceroute and ping. (Source Code)
GPL-2.0C - Sysdig - Capture system state and activity from a running Linux instance, then save, filter and analyze. (Source Code)
Apache-2.0Docker/Lua/C - Wireshark - The world's foremost network protocol analyzer. (Source Code)
GPL-2.0C
- grml - Bootable Debian Live CD with powerful CLI tools. (Source Code)
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-23 23:37:17
@ 5d4b6c8d:8a1c1ee3
2025-05-23 23:37:17@grayruby loves to blow up the odds of various sports markets at Predyx. Well, the jig is up, because I finally managed to deposit some sats at BetPlay where I can leverage the mismatched odds.
So, I've now locked in guaranteed wins on the 49ers winning the Super Bowl and the Panthers winning the Stanley Cup.
https://stacker.news/items/987847
-
 @ 6d5c826a:4b27b659
2025-05-23 21:52:06
@ 6d5c826a:4b27b659
2025-05-23 21:52:06- Docker Compose - Define and run multi-container Docker applications. (Source Code)
Apache-2.0Go - Docker Swarm - Manage cluster of Docker Engines. (Source Code)
Apache-2.0Go - Docker - Platform for developers and sysadmins to build, ship, and run distributed applications. (Source Code)
Apache-2.0Go - LXC - Userspace interface for the Linux kernel containment features. (Source Code)
GPL-2.0C - LXD - Container "hypervisor" and a better UX for LXC. (Source Code)
Apache-2.0Go - OpenVZ - Container-based virtualization for Linux. (Source Code)
GPL-2.0C - Podman - Daemonless container engine for developing, managing, and running OCI Containers on your Linux System. Containers can either be run as root or in rootless mode. Simply put:
alias docker=podman. (Source Code)Apache-2.0Go - Portainer Community Edition - Simple management UI for Docker. (Source Code)
ZlibGo - systemd-nspawn - Lightweight, chroot-like, environment to run an OS or command directly under systemd. (Source Code)
GPL-2.0C
- Docker Compose - Define and run multi-container Docker applications. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:49:50
@ 6d5c826a:4b27b659
2025-05-23 21:49:50- Consul - Consul is a tool for service discovery, monitoring and configuration. (Source Code)
MPL-2.0Go - etcd - Distributed K/V-Store, authenticating via SSL PKI and a REST HTTP Api for shared configuration and service discovery. (Source Code)
Apache-2.0Go - ZooKeeper - ZooKeeper is a centralized service for maintaining configuration information, naming, providing distributed synchronization, and providing group services. (Source Code)
Apache-2.0Java/C++
- Consul - Consul is a tool for service discovery, monitoring and configuration. (Source Code)
-
 @ c1e9ab3a:9cb56b43
2025-05-09 23:10:14
@ c1e9ab3a:9cb56b43
2025-05-09 23:10:14I. Historical Foundations of U.S. Monetary Architecture
The early monetary system of the United States was built atop inherited commodity money conventions from Europe’s maritime economies. Silver and gold coins—primarily Spanish pieces of eight, Dutch guilders, and other foreign specie—formed the basis of colonial commerce. These units were already integrated into international trade and piracy networks and functioned with natural compatibility across England, France, Spain, and Denmark. Lacking a centralized mint or formal currency, the U.S. adopted these forms de facto.
As security risks and the practical constraints of physical coinage mounted, banks emerged to warehouse specie and issue redeemable certificates. These certificates evolved into fiduciary media—claims on specie not actually in hand. Banks observed over time that substantial portions of reserves remained unclaimed for years. This enabled fractional reserve banking: issuing more claims than reserves held, so long as redemption demand stayed low. The practice was inherently unstable, prone to panics and bank runs, prompting eventual centralization through the formation of the Federal Reserve in 1913.
Following the Civil War and unstable reinstatements of gold convertibility, the U.S. sought global monetary stability. After World War II, the Bretton Woods system formalized the U.S. dollar as the global reserve currency. The dollar was nominally backed by gold, but most international dollars were held offshore and recycled into U.S. Treasuries. The Nixon Shock of 1971 eliminated the gold peg, converting the dollar into pure fiat. Yet offshore dollar demand remained, sustained by oil trade mandates and the unique role of Treasuries as global reserve assets.
II. The Structure of Fiduciary Media and Treasury Demand
Under this system, foreign trade surpluses with the U.S. generate excess dollars. These surplus dollars are parked in U.S. Treasuries, thereby recycling trade imbalances into U.S. fiscal liquidity. While technically loans to the U.S. government, these purchases act like interest-only transfers—governments receive yield, and the U.S. receives spendable liquidity without principal repayment due in the short term. Debt is perpetually rolled over, rarely extinguished.
This creates an illusion of global subsidy: U.S. deficits are financed via foreign capital inflows that, in practice, function more like financial tribute systems than conventional debt markets. The underlying asset—U.S. Treasury debt—functions as the base reserve asset of the dollar system, replacing gold in post-Bretton Woods monetary logic.
III. Emergence of Tether and the Parastatal Dollar
Tether (USDT), as a private issuer of dollar-denominated tokens, mimics key central bank behaviors while operating outside the regulatory perimeter. It mints tokens allegedly backed 1:1 by U.S. dollars or dollar-denominated securities (mostly Treasuries). These tokens circulate globally, often in jurisdictions with limited banking access, and increasingly serve as synthetic dollar substitutes.
If USDT gains dominance as the preferred medium of exchange—due to technological advantages, speed, programmability, or access—it displaces Federal Reserve Notes (FRNs) not through devaluation, but through functional obsolescence. Gresham’s Law inverts: good money (more liquid, programmable, globally transferable USDT) displaces bad (FRNs) even if both maintain a nominal 1:1 parity.
Over time, this preference translates to a systemic demand shift. Actors increasingly use Tether instead of FRNs, especially in global commerce, digital marketplaces, or decentralized finance. Tether tokens effectively become shadow base money.
IV. Interaction with Commercial Banking and Redemption Mechanics
Under traditional fractional reserve systems, commercial banks issue loans denominated in U.S. dollars, expanding the money supply. When borrowers repay loans, this destroys the created dollars and contracts monetary elasticity. If borrowers repay in USDT instead of FRNs:
- Banks receive a non-Fed liability (USDT).
- USDT is not recognized as reserve-eligible within the Federal Reserve System.
- Banks must either redeem USDT for FRNs, or demand par-value conversion from Tether to settle reserve requirements and balance their books.
This places redemption pressure on Tether and threatens its 1:1 peg under stress. If redemption latency, friction, or cost arises, USDT’s equivalence to FRNs is compromised. Conversely, if banks are permitted or compelled to hold USDT as reserve or regulatory capital, Tether becomes a de facto reserve issuer.
In this scenario, banks may begin demanding loans in USDT, mirroring borrower behavior. For this to occur sustainably, banks must secure Tether liquidity. This creates two options: - Purchase USDT from Tether or on the secondary market, collateralized by existing fiat. - Borrow USDT directly from Tether, using bank-issued debt as collateral.
The latter mirrors Federal Reserve discount window operations. Tether becomes a lender of first resort, providing monetary elasticity to the banking system by creating new tokens against promissory assets—exactly how central banks function.
V. Structural Consequences: Parallel Central Banking
If Tether begins lending to commercial banks, issuing tokens backed by bank notes or collateralized debt obligations: - Tether controls the expansion of broad money through credit issuance. - Its balance sheet mimics a central bank, with Treasuries and bank debt as assets and tokens as liabilities. - It intermediates between sovereign debt and global liquidity demand, replacing the Federal Reserve’s open market operations with its own issuance-redemption cycles.
Simultaneously, if Tether purchases U.S. Treasuries with FRNs received through token issuance, it: - Supplies the Treasury with new liquidity (via bond purchases). - Collects yield on government debt. - Issues a parallel form of U.S. dollars that never require redemption—an interest-only loan to the U.S. government from a non-sovereign entity.
In this context, Tether performs monetary functions of both a central bank and a sovereign wealth fund, without political accountability or regulatory transparency.
VI. Endgame: Institutional Inversion and Fed Redundancy
This paradigm represents an institutional inversion:
- The Federal Reserve becomes a legacy issuer.
- Tether becomes the operational base money provider in both retail and interbank contexts.
- Treasuries remain the foundational reserve asset, but access to them is mediated by a private intermediary.
- The dollar persists, but its issuer changes. The State becomes a fiscal agent of a decentralized financial ecosystem, not its monetary sovereign.
Unless the Federal Reserve reasserts control—either by absorbing Tether, outlawing its instruments, or integrating its tokens into the reserve framework—it risks becoming irrelevant in the daily function of money.
Tether, in this configuration, is no longer a derivative of the dollar—it is the dollar, just one level removed from sovereign control. The future of monetary sovereignty under such a regime is post-national and platform-mediated.
-
 @ b8851a06:9b120ba1
2025-05-09 22:54:43
@ b8851a06:9b120ba1
2025-05-09 22:54:43The global financial system is creaking under its own weight. The IMF is urging banks to shore up capital, cut risk, and brace for impact. Basel III is their answer, a last-ditch effort to reinforce a brittle foundation.
But behind the scenes, a quieter revolution is under way.
Bitcoin, the world’s first stateless digital asset, is no longer on the sidelines. It’s entering the Basel conversation: not by invitation, but by inevitability.
Basel III: The System’s Self-Diagnosis
Basel III is more than a technical rulebook. It’s a confession: an admission that the global banking system is vulnerable. Created in the aftermath of 2008, it calls for: • Stronger capital reserves: So banks can survive losses. • Lower leverage: To reduce the domino effect of overexposure. • Liquidity buffers: To weather short-term shocks without collapsing.
But here’s the kicker: these rules are hostile to anything outside the fiat system. Bitcoin gets hit with a punitive 1,250% risk weight. That means for every $1 of exposure, banks must hold $1 in capital. The message from regulators? “You can hold Bitcoin, but you’ll pay for it.”
Yet that fear: based framing misses a bigger truth: Bitcoin doesn’t just survive in this environment. It thrives in it.
Bitcoin: A Parallel System, Built on Hard Rules
Where Basel III imposes “fiat discipline” from the top down, Bitcoin enforces it from the bottom up: with code, math, and transparency.
Bitcoin is not just a hedge. It’s a structural antidote to systemic fragility.
Volatility: A Strategic Asset
Yes, Bitcoin is volatile. But in a system that devalues fiat on a schedule, volatility is simply the cost of freedom. Under Basel III, banks are expected to build capital buffers during economic expansions.
What asset allows you to build those buffers faster than Bitcoin in a bull market?
When the cycle turns, those reserves act as shock absorbers: converting volatility into resilience. It’s anti-fragility in motion.
Liquidity: Real, Deep, and Global
Bitcoin settled over $19 trillion in transactions in 2024. That’s not hypothetical liquidity. it’s real, measurable flow. Unlike traditional high-quality liquid assets (HQLAs), Bitcoin is: • Available 24/7 • Borderless • Not dependent on central banks
By traditional definitions, Bitcoin is rapidly qualifying for HQLA status. Even if regulators aren’t ready to admit it.
Diversification: Breaking the Fiat Dependency
Basel III is designed to pull banks back into the fiat matrix. But Bitcoin offers an escape hatch. Strategic Bitcoin reserves are not about speculation, they’re insurance. For family offices, institutions, and sovereign funds, Bitcoin is the lifeboat when the fiat ship starts taking on water.
Regulatory Realignment: The System Reacts
The Basel Committee’s new rules on crypto exposures went live in January 2025. Around the world, regulators are scrambling to define their stance. Every new restriction placed on Bitcoin only strengthens its legitimacy, as more institutions ask: Why so much resistance, if it’s not a threat?
Bitcoin doesn’t need permission. It’s already being adopted by over 150 public companies, forward-looking states, and a new class of self-sovereign individuals.
Conclusion: The Real Question
This isn’t just about Bitcoin fitting into Basel III.
The real question is: How long can Basel III remain relevant in a world where Bitcoin exists?
Bitcoin is not the risk. It’s the reality check. And it might just be the strongest capital buffer the system has ever seen.
Gradually then suddenly.
-
 @ 3c389c8f:7a2eff7f
2025-05-23 21:35:30
@ 3c389c8f:7a2eff7f
2025-05-23 21:35:30Web:
https://shopstr.store/
https://cypher.space/
https://plebeian.market/
Mobile:
https://www.amethyst.social/
-
 @ 6d5c826a:4b27b659
2025-05-23 21:49:30
@ 6d5c826a:4b27b659
2025-05-23 21:49:30- DD-WRT - A Linux-based firmware for wireless routers and access points, originally designed for the Linksys WRT54G series. (Source Code)
GPL-2.0C - OpenWrt - A Linux-based router featuring Mesh networking, IPS via snort and AQM among many other features. (Source Code)
GPL-2.0C - OPNsense - An open source FreeBSD-based firewall and router with traffic shaping, load balancing, and virtual private network capabilities. (Source Code)
BSD-2-ClauseC/PHP - pfSense CE - Free network firewall distribution, based on the FreeBSD operating system with a custom kernel and including third party free software packages for additional functionality. (Source Code)
Apache-2.0Shell/PHP/Other
- DD-WRT - A Linux-based firmware for wireless routers and access points, originally designed for the Linksys WRT54G series. (Source Code)
-
 @ 3c389c8f:7a2eff7f
2025-05-23 21:27:26
@ 3c389c8f:7a2eff7f
2025-05-23 21:27:26Clients:
https://untype.app
https://habla.news
https://yakihonne.com
https://cypher.space
https://highlighter.com
https://pareto.space/en
https://comet.md/
Plug Ins:
https://github.com/jamesmagoo/nostr-writer
https://threenine.co.uk/products/obstrlish
Content Tagging:
https://labelmachine.org
https://ontolo.social
Blog-like Display and Personal Pages:
https://orocolo.me
https://npub.pro
Personal Notes and Messaging:
https://app.flotilla.social There's an app, too!
https://nosbin.com
RSS Readers:
https://nostrapps.com/noflux
https://nostrapps.com/narr
https://nostrapps.com/feeder
-
 @ 6d5c826a:4b27b659
2025-05-23 21:49:12
@ 6d5c826a:4b27b659
2025-05-23 21:49:12- Remmina - Feature-rich remote desktop application for linux and other unixes. (Source Code)
GPL-2.0C - Tiger VNC - High-performance, multi-platform VNC client and server. (Source Code)
GPL-2.0C++ - X2go - X2Go is an open source remote desktop software for Linux that uses the NoMachine/NX technology protocol. (Source Code)
GPL-2.0Perl
- Remmina - Feature-rich remote desktop application for linux and other unixes. (Source Code)
-
 @ 86611181:9fc27ad7
2025-05-23 20:31:44
@ 86611181:9fc27ad7
2025-05-23 20:31:44It's time to secure user data in your identity system This post was also published with the Industry Association of Privacy Professionals.
It seems like every day there is a new report of a major personal data breach. In just the past few months, Neiman Marcus, Ticketmaster, Evolve Bank, TeamViewer, Hubspot, and even the IRS have been affected.
The core issue is that user data is commonly spread across multiple systems that are increasingly difficult to fully secure, including database user tables, data warehouses and unstructured documents.
Most enterprises are already running an incredibly secure and hardened identity system to manage customer login and authorization, commonly referred to as a customer identity access management system. Since identity systems manage customer sign-up and sign-in, they typically contain customer names, email addresses, and phone numbers for multifactor authentication. Commercial CIAMs provide extensive logging, threat detection, availability and patch management.
Identity systems are highly secure and already store customers' personally identifiable information, so it stands to reason enterprises should consider identity systems to manage additional PII fields.
Identity systems are designed to store numerous PII fields and mask the fields for other systems. The Liberty Project developed the protocols that became Security Assertion Markup Language 2.0, the architecture at the core of CIAM systems, 20 years ago, when I was its chief technology officer. SAML 2.0 was built so identity data would be fully secure, and opaque tokens would be shared with other systems. Using tokens instead of actual user data is a core feature of identity software that can be used to fully secure user data across applications.
Most modern identity systems support adding additional customer fields, so it is easy to add new fields like Social Security numbers and physical addresses. Almost like a database, some identity systems even support additional tables and images.
A great feature of identity systems is that they often provide a full suite of user interface components for users to register, login and manage their profile fields. Moving fields like Social Security numbers from your database to your identity system means the identity system can fully manage the process of users entering, viewing and editing the field, and your existing application and database become descoped from managing sensitive data.
With sensitive fields fully isolated in an identity system and its user interface components, the identity system can provide for cumbersome and expensive compliance with standards such as the Health Insurance Portability and Accountability Act for medical data and the Payment Card Industry Data Security Standard for payment data, saving the time and effort to achieve similar compliance in your application.
There are, of course, applications that require sensitive data, such as customer service systems and data warehouses. Identity systems use a data distribution standard called System for Cross-domain Identity Management 2.0 to copy user data to other systems. The SCIM is a great standard to help manage compliance such as "right to be forgotten," because it can automatically delete customer data from other systems when a customer record is deleted from the identity system.
When copying customer data from an identity system to another application, consider anonymizing or masking fields. For example, anonymizing a birthdate into an age range when copying a customer record into a data warehouse can descope the data warehouse from containing personal information.
Most enterprises already run an Application Programming Interface Gateway to manage web services between systems. By combining an API Gateway with the identity system's APIs, it becomes very easy to automatically anonymize and mask customer data fields before they are copied into other systems.
A new set of companies including Baffle, Skyflow, and Piiano have introduced services that combine the governance and field management features of an identity system with extensive field masking. Since these systems do not offer the authentication and authorization features of an identity system, it's important to balance the additional features as they introduce an additional threat surface with PII storage and permissions.
PII sprawl is an increasing liability for companies. The most secure, compliant and flexible central data store to manage PII is the existing CIAM and API Gateway infrastructure that enterprises have already deployed.
Move that customer data into your identity system and lock it down. https://peter.layer3.press/articles/3c6912eb-404a-4630-9fe9-fd1bd23cfa64
-
 @ 6d5c826a:4b27b659
2025-05-23 21:48:56
@ 6d5c826a:4b27b659
2025-05-23 21:48:56- ActiveMQ - Java message broker. (Source Code)
Apache-2.0Java - BeanstalkD - A simple, fast work queue. (Source Code)
MITC - Gearman - Fast multi-language queuing/job processing platform. (Source Code)
BSD-3-ClauseC++ - NSQ - A realtime distributed messaging platform. (Source Code)
MPL-2.0Go - ZeroMQ - Lightweight queuing system. (Source Code)
GPL-3.0C++
- ActiveMQ - Java message broker. (Source Code)
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-23 19:32:28
@ 5d4b6c8d:8a1c1ee3
2025-05-23 19:32:28https://primal.net/e/nevent1qvzqqqqqqypzp6dtxy5uz5yu5vzxdtcv7du9qm9574u5kqcqha58efshkkwz6zmdqqszj207pl0eqkgld9vxknxamged64ch2x2zwhszupkut5v46vafuhg9833px
Some of my colleagues were talking about how they're even more scared of RFK Jr. than they are of Trump. I hope he earns it.
https://stacker.news/items/987685
-
 @ b04082ac:29b5c55b
2025-05-08 14:35:02
@ b04082ac:29b5c55b
2025-05-08 14:35:02Money has always been more than a medium of exchange. It reflects what societies value, how they organize trust, and what they choose to remember. This article explores the idea that money functions as a form of collective memory, and how Bitcoin may be restoring this role in a new way.

The Asante Example
In the Asante Empire, which flourished in West Africa during the 18th and 19th centuries, gold dust served as the primary medium of exchange. To measure it, traders used ornate spoons made of brass. These spoons were often carved with birds, animals, or abstract symbols. They were not currency themselves, but tools used to handle gold dust accurately.
Importantly, these spoons also carried meaning. Symbols and proverbs embedded in the spoons conveyed lessons about honesty, community, and continuity. For example, the Sankofa bird, shown turning its head backward to retrieve an egg from its back, represented the proverb, “It is not wrong to go back for that which you have forgotten.” This was a reminder to learn from the past.

The spoons reflect an understanding that money and its instruments are not just practical tools. They are cultural artifacts that store shared values. In the Asante context, even measurement was ritualized and tied to ethics and memory.
Money as a Cultural Medium
This connection between money and cultural meaning is not unique to the Asante Empire. Modern fiat currencies also carry symbols, phrases, and designs that reflect national identity and political values.
The U.S. dollar includes Latin phrases and national symbols meant to convey stability and purpose. The British pound features royal iconography, reinforcing the idea of continuity and sovereignty. When the euro was introduced, it deliberately avoided specific national references. Itsdesign used bridges and windowsto suggest openness and cooperation across the continent.

These design choices show that societies still embed meaning into their money. Even in a digital or fiat context, money is used to transmit a story about who we are, where authority lies, and what we value.
The Fragility of Fiat Memory
While fiat money carries cultural symbols, the narratives behind those symbols can be fragile.
In 2021, the central bank of the Philippines removed democratic leaders from its banknotes,triggering public criticism. In the United States, attempts to replace Andrew Jackson with Harriet Tubman on the $20 billfaced repeated delays. These examples show how political control over money includes control over what stories are told and remembered.

Unlike objects passed down through generations, fiat memory can be edited or erased. In this sense, it is vulnerable. The meaning encoded in fiat systems can shift depending on who holds power.
Bitcoin as a New Form of Memory
Bitcoin is described as digital money. But it also introduces a different model of how societies can record value and preserve meaning.
The Bitcoin network launched in 2009 with a small message embedded in its first block: “Chancellor on brink of second bailout for banks.” This was a reference to a newspaper headline that day and a clear sign of protest against financial bailouts, centralized monetary policy, and forever wars.

This moment marked the beginning of a system where memory is stored differently. Instead of relying on governments or institutions, Bitcoin stores its history on a public ledger maintained by a decentralized network of participants. Its memory is not symbolic or political; it is structural. Every transaction, every block, is preserved through time-stamped computation and consensus.
No single authority can change it. The rules are clear and publicly auditable. In this way, Bitcoin offers a version of money where memory is both neutral and resilient.
Cultural Expression and Community Values
Even though Bitcoin lacks the traditional symbols found on banknotes, it has developed its own culture. Phrases like “Don’t trust, verify” or “Stay humble, stack sats” are shared widely in the Bitcoin community. These ideas reflect a focus on self-responsibility, verification, and long-term thinking.
These proverbs can be compared to the carved messages on the Asante spoons. While the contexts are very different, the underlying idea is similar: a community using language and symbols to reinforce its shared values.
Bitcoin also has a well established and growing art scene. Bitcoin conferences often feature dedicated sections for art inspired by the protocol and its culture. Statues of Satoshi Nakamoto have been installed in cities like Budapest, Lugano, and Fornelli. These physical works reflect the desire to link Bitcoin’s abstract values to something tangible.

Looking Back to Look Forward
The Asante example helps us see that money has long been tied to memory and meaning. Their spoons were practical tools but also cultural anchors. Bitcoin, while new and digital, may be playing a similar role.
Instead of relying on political symbols or national myths, Bitcoin uses code, transparency, and global consensus to create trust. In doing so, it offers a way to preserve economic memory that does not depend on power or politics.
It’s still early to know what kind of legacy Bitcoin will leave. But if it succeeds, it may not just change how money works. It may also change how civilizations remember.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:48:36
@ 6d5c826a:4b27b659
2025-05-23 21:48:36- aptly - Swiss army knife for Debian repository management. (Source Code)
MITGo - fpm - Versatile multi format package creator. (Source Code)
MITRuby - omnibus-ruby - Easily create full-stack installers for your project across a variety of platforms.
Apache-2.0Ruby - tito - Builds RPMs for git-based projects.
GPL-2.0Python
- aptly - Swiss army knife for Debian repository management. (Source Code)
-
 @ 40bdcc08:ad00fd2c
2025-05-06 14:24:22
@ 40bdcc08:ad00fd2c
2025-05-06 14:24:22Introduction
Bitcoin’s
OP_RETURNopcode, a mechanism for embedding small data in transactions, has ignited a significant debate within the Bitcoin community. Originally designed to support limited metadata while preserving Bitcoin’s role as a peer-to-peer electronic cash system,OP_RETURNis now at the center of proposals that could redefine Bitcoin’s identity. The immutable nature of Bitcoin’s timechain makes it an attractive platform for data storage, creating tension with those who prioritize its monetary function. This discussion, particularly around Bitcoin Core pull request #32406 (GitHub PR #32406), highlights a critical juncture for Bitcoin’s future.What is
OP_RETURN?Introduced in 2014,
OP_RETURNallows users to attach up to 80 bytes of data to a Bitcoin transaction. Unlike other transaction outputs,OP_RETURNoutputs are provably unspendable, meaning they don’t burden the Unspent Transaction Output (UTXO) set—a critical database for Bitcoin nodes. This feature was a compromise to provide a standardized, less harmful way to include metadata, addressing earlier practices that embedded data in ways that bloated the UTXO set. The 80-byte limit and restriction to oneOP_RETURNoutput per transaction are part of Bitcoin Core’s standardness rules, which guide transaction relay and mining but are not enforced by the network’s consensus rules (Bitcoin Stack Exchange).Standardness vs. Consensus Rules
Standardness rules are Bitcoin Core’s default policies for relaying and mining transactions. They differ from consensus rules, which define what transactions are valid across the entire network. For
OP_RETURN: - Consensus Rules: AllowOP_RETURNoutputs with data up to the maximum script size (approximately 10,000 bytes) and multiple outputs per transaction (Bitcoin Stack Exchange). - Standardness Rules: LimitOP_RETURNdata to 80 bytes and one output per transaction to discourage excessive data storage and maintain network efficiency.Node operators can adjust these policies using settings like
-datacarrier(enables/disablesOP_RETURNrelay) and-datacarriersize(sets the maximum data size, defaulting to 83 bytes to account for theOP_RETURNopcode and pushdata byte). These settings allow flexibility but reflect Bitcoin Core’s default stance on limiting data usage.The Proposal: Pull Request #32406
Bitcoin Core pull request #32406, proposed by developer instagibbs, seeks to relax these standardness restrictions (GitHub PR #32406). Key changes include: - Removing Default Size Limits: The default
-datacarriersizewould be uncapped, allowing largerOP_RETURNdata without a predefined limit. - Allowing Multiple Outputs: The restriction to oneOP_RETURNoutput per transaction would be lifted, with the total data size across all outputs subject to a configurable limit. - Deprecating Configuration Options: The-datacarrierand-datacarriersizesettings are marked as deprecated, signaling potential removal in future releases, which could limit node operators’ ability to enforce custom restrictions.This proposal does not alter consensus rules, meaning miners and nodes can already accept transactions with larger or multiple
OP_RETURNoutputs. Instead, it changes Bitcoin Core’s default relay policy to align with existing practices, such as miners accepting non-standard transactions via services like Marathon Digital’s Slipstream (CoinDesk).Node Operator Flexibility
Currently, node operators can customize
OP_RETURNhandling: - Default Settings: Relay transactions with oneOP_RETURNoutput up to 80 bytes. - Custom Settings: Operators can disableOP_RETURNrelay (-datacarrier=0) or adjust the size limit (e.g.,-datacarriersize=100). These options remain in #32406 but are deprecated, suggesting that future Bitcoin Core versions might not support such customization, potentially standardizing the uncapped policy.Arguments in Favor of Relaxing Limits
Supporters of pull request #32406 and similar proposals argue that the current restrictions are outdated and ineffective. Their key points include: - Ineffective Limits: Developers bypass the 80-byte limit using methods like Inscriptions, which store data in other transaction parts, often at higher cost and inefficiency (BitcoinDev Mailing List). Relaxing
OP_RETURNcould channel data into a more efficient format. - Preventing UTXO Bloat: By encouragingOP_RETURNuse, which doesn’t affect the UTXO set, the proposal could reduce reliance on harmful alternatives like unspendable Taproot outputs used by projects like Citrea’s Clementine bridge. - Supporting Innovation: Projects like Citrea require more data (e.g., 144 bytes) for security proofs, and relaxed limits could enable new Layer 2 solutions (CryptoSlate). - Code Simplification: Developers like Peter Todd argue that these limits complicate Bitcoin Core’s codebase unnecessarily (CoinGeek). - Aligning with Practice: Miners already process non-standard transactions, and uncapping defaults could improve fee estimation and reduce reliance on out-of-band services, as noted by ismaelsadeeq in the pull request discussion.In the GitHub discussion, developers like Sjors and TheCharlatan expressed support (Concept ACK), citing these efficiency and innovation benefits.
Arguments Against Relaxing Limits
Opponents, including prominent developers and community members, raise significant concerns about the implications of these changes: - Deviation from Bitcoin’s Purpose: Critics like Luke Dashjr, who called the proposal “utter insanity,” argue that Bitcoin’s base layer should prioritize peer-to-peer cash, not data storage (CoinDesk). Jason Hughes warned it could turn Bitcoin into a “worthless altcoin” (BeInCrypto). - Blockchain Bloat: Additional data increases the storage and processing burden on full nodes, potentially making node operation cost-prohibitive and threatening decentralization (CryptoSlate). - Network Congestion: Unrestricted data could lead to “spam” transactions, raising fees and hindering Bitcoin’s use for financial transactions. - Risk of Illicit Content: The timechain’s immutability means data, including potentially illegal or objectionable content, is permanently stored on every node. The 80-byte limit acts as a practical barrier, and relaxing it could exacerbate this issue. - Preserving Consensus: Developers like John Carvalho view the limits as a hard-won community agreement, not to be changed lightly.
In the pull request discussion, nsvrn and moth-oss expressed concerns about spam and centralization, advocating for gradual changes. Concept NACKs from developers like wizkid057 and Luke Dashjr reflect strong opposition.
Community Feedback
The GitHub discussion for pull request #32406 shows a divided community: - Support (Concept ACK): Sjors, polespinasa, ismaelsadeeq, miketwenty1, TheCharlatan, Psifour. - Opposition (Concept NACK): wizkid057, BitcoinMechanic, Retropex, nsvrn, moth-oss, Luke Dashjr. - Other: Peter Todd provided a stale ACK, indicating partial or outdated support.
Additional discussions on the BitcoinDev mailing list and related pull requests (e.g., #32359 by Peter Todd) highlight similar arguments, with #32359 proposing a more aggressive removal of all
OP_RETURNlimits and configuration options (GitHub PR #32359).| Feedback Type | Developers | Key Points | |---------------|------------|------------| | Concept ACK | Sjors, ismaelsadeeq, others | Improves efficiency, supports innovation, aligns with mining practices. | | Concept NACK | Luke Dashjr, wizkid057, others | Risks bloat, spam, centralization, and deviation from Bitcoin’s purpose. | | Stale ACK | Peter Todd | Acknowledges proposal but with reservations or outdated support. |
Workarounds and Their Implications
The existence of workarounds, such as Inscriptions, which exploit SegWit discounts to embed data, is a key argument for relaxing
OP_RETURNlimits. These methods are costlier and less efficient, often costing more thanOP_RETURNfor data under 143 bytes (BitcoinDev Mailing List). Supporters argue that formalizing largerOP_RETURNdata could streamline these use cases. Critics, however, see workarounds as a reason to strengthen, not weaken, restrictions, emphasizing the need to address underlying incentives rather than accommodating bypasses.Ecosystem Pressures
External factors influence the debate: - Miners: Services like Marathon Digital’s Slipstream process non-standard transactions for a fee, showing that market incentives already bypass standardness rules. - Layer 2 Projects: Citrea’s Clementine bridge, requiring more data for security proofs, exemplifies the demand for relaxed limits to support innovative applications. - Community Dynamics: The debate echoes past controversies, like the Ordinals debate, where data storage via inscriptions raised similar concerns about Bitcoin’s purpose (CoinDesk).
Bitcoin’s Identity at Stake
The
OP_RETURNdebate is not merely technical but philosophical, questioning whether Bitcoin should remain a focused monetary system or evolve into a broader data platform. Supporters see relaxed limits as a pragmatic step toward efficiency and innovation, while opponents view them as a risk to Bitcoin’s decentralization, accessibility, and core mission. The community’s decision will have lasting implications, affecting node operators, miners, developers, and users.Conclusion
As Bitcoin navigates this crossroads, the community must balance the potential benefits of relaxed
OP_RETURNlimits—such as improved efficiency and support for new applications—against the risks of blockchain bloat, network congestion, and deviation from its monetary roots. The ongoing discussion, accessible via pull request #32406 on GitHub (GitHub PR #32406). Readers are encouraged to explore the debate and contribute to ensuring that any changes align with Bitcoin’s long-term goals as a decentralized, secure, and reliable system. -
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 6d5c826a:4b27b659
2025-05-23 21:48:21
@ 6d5c826a:4b27b659
2025-05-23 21:48:21- CapRover - Build your own PaaS in a few minutes. (Demo, Source Code)
Apache-2.0Docker/Nodejs - Coolify - An open-source & self-hostable Heroku / Netlify alternative (and even more). (Source Code)
Apache-2.0Docker - Dokku - An open-source PaaS (alternative to Heroku). (Source Code)
MITDocker/Shell/Go/deb - fx - A tool to help you do Function as a Service with painless on your own servers.
MITGo - Kubero - A self-hosted Heroku PaaS alternative for Kubernetes that implements GitOps. (Demo, Source Code)
GPL-3.0K8S/Nodejs/Go - LocalStack - LocalStack is a fully functional local AWS cloud stack. This includes Lambda for serverless computation. (Source Code)
Apache-2.0Python/Docker/K8S - Nhost - Firebase Alternative with GraphQL. Get a database and backend configured and ready in minutes. (Source Code)
MITDocker/Nodejs/Go - OpenFaaS - Serverless Functions Made Simple for Docker & Kubernetes. (Source Code)
MITGo - Tau - Easily build Cloud Computing Platforms with features like Serverless WebAssembly Functions, Frontend Hosting, CI/CD, Object Storage, K/V Database, and Pub-Sub Messaging. (Source Code)
BSD-3-ClauseGo/Rust/Docker - Trusted-CGI - Lightweight self-hosted lambda/applications/cgi/serverless-functions platform.
MITGo/deb/Docker
- CapRover - Build your own PaaS in a few minutes. (Demo, Source Code)
-
 @ 3c389c8f:7a2eff7f
2025-05-23 18:23:28
@ 3c389c8f:7a2eff7f
2025-05-23 18:23:28I've sporadically been trying to spend some time familiarizing myself with Nostr marketplace listings and the clients that support them. I have been pleased with what I have encountered. The clients are simple to use, and people have been receptive to transacting with me. I've sold items to both people whom I consider to be close contacts, as well as to people that I barely know.
My first attempt was close to 2 years ago, when I listed one pound bags of coffee for sale. If I remember correctly, there was only one marketplace client then, and it only had support for extension signing. At the time, my old laptop had just died so I couldn't really interact with my listings through that client. (I have never had much luck with extensions on mobile browsers, so I have never attempted to use one for Nostr.) Instead, I used Amethyst to list my product and exchange messages with potential buyers. The Amethyst approach to handling different Nostr events is brilliant to me. You can do some part of each thing but not all. I view it as great introduction to what Nostr is capable of doing and a gateway to discovering other clients. Marketplace listings on Amethyst are handled in that fashion. You can list products for sale. You can browse and inquire about products listed by your contacts or by a more "global" view, which in the case of Nostr, would be products listed by anyone who publishes their listings to any of the relays that I connect with to read. There is no delete option, should a product sell out, and there is no direct purchase option. All sales need to be negotiated through direct messages. Though it has limited functionality, the system works great for items that will be listed for repeated sale, such as my coffee. If one were to list a one-off item and sell it, the flow to delete the listing would be easy enough. Copy the event ID, visit delete.nostr.com , and remove the product. Should there be a price change, it would be necessary to visit a full marketplace client to edit the listing, though one could easily delete and start over as well. Anyway, much to my surprise I sold more coffee than I had anticipated through that listing. People were eager to try out the feature and support a small business. This was an awesome experience and I see no reason to avoid buying or selling products on Nostr, even if the only client available to you is Amethyst. (Which I think might be the only mobile app with marketplace support.) It is completely manageable.
Later, I tried to list a pair of nearly new shoes. Those did not sell. I have a sneaking suspicion that there were very few people that wore size USw6 shoes using Nostr at the time. Even though no one wanted my shoes, I still ended up having some interesting conversations about different styles of running shoes, boots, and other footwear talk. I can't call the listing a total bust, even though I ended up deleting the listing and donating those shoes to the YWCA. After some number of months watching and reading about development in the Nostr marketplace space, I decided to try again.
This second approach, I started with niche rubber duckies that, for reasons unbeknownst to most, I just happen to have an abundance of. It occurred to me that day that I would most likely be creating most of my listings via mobile app since that is also my main method of taking pictures these days. I could sync or send them, but realistically it's just adding extra steps for me. I listed my ducks with Amethyst (all of which are currently still available, surprise, surprise.). I immediately went to check how the listing renders in the marketplace clients. There are 2 where I can view it, and the listing looks nice, clean, organized in both places. That alone is reason enough to get excited about selling on Nostr. Gone are the days of "this item is cross-posted to blah, blah, blah" lest risk being kicked out of the seller groups on silo'd platforms.
Knowing I can't take it personally that literally no one else on Nostr has an affinity for obscure rubber ducks (that they are willing to admit), I leave my duckies listed and move on. My next listing is for artisan bracelets. Ones that I love to make. I made my mobile listing, checked it across clients and this time I noticed that shopstr.store is collecting my listings into a personal seller profile, like a little shop. I spent some time setting up the description and banner, and now it looks really nice. This is great, since the current site acts as an open and categorized market for all sellers. Maybe someone will see the bracelets while browsing the clothing category and stumble upon the rubber ducky of their dreams in the process. That hasn't happened yet, but I was pretty jazzed to sell a few bracelets right away. Most of the sale and exchange happened via DM, for which I switched to Flotilla because it just handles messaging solidly for me. I made some bracelets, waited a few weeks, then visited Shopstr again to adjust the price. That worked out super well. I noticed that a seller can also list in their preferred currency, which is very cool. Meanwhile, back to my social feed, I can see my listing posted again since there was an edit. While not always the best thing to happen with edits, it is great that it happens with marketplace listings. It removes all the steps of announcing a price reduction, which would be handy for any serious seller. I am very happy with the bracelet experience, and I will keep that listing active and reasonably up to date for as long as any interest arises. Since this has all gone so well, I've opted to continue listing saleable items to Nostr first for a few days to a few weeks prior to marketing them anywhere else.
Looking at my listings on cypher.space, I can see that this client is tailored more towards people who are very passionate about a particular set of things. I might not fall into this category but my listings still look very nice displayed with my writing, transposed poetry, and recipes. I could see this being a great space for truly devotional hobbyists or sellers who are both deeply knowledgeable about their craft and also actively selling. My experience with all 3 of these marketplace-integrated clients had been positive and I would say that if you are considering selling on Nostr, it is worth the effort.
As some sidenotes:
-
I am aware that Shopstr has been built to be self-hosted and anyone interested in selling for the long term should at least consider doing so. This will help reduce the chances of Nostr marketplaces centralizing into just another seller-silo.
-
Plebeian Market is out there, too. From the best I could tell, even though this is a Nostr client, those listings are a different kind than listings made from the other clients referenced here. I like the layout and responsiveness of the site but I opted not to try it out for now. Cross-posting has been the bane of online selling for me for quite some time. If they should migrate to an interoperable listing type (which I think I read may happen in the future), I will happily take that for a spin, too.
-
My only purchase over Nostr marketplaces so far was some vinyls, right around the time I had listed my coffee. It went well, the seller was great to work with, everything arrived in good shape. I have made some other purchases through Nostr contacts, but those were conversations that lead to non-Nostr seller sites. I check the marketplace often, though, for things I may want/need. The listings are changing and expanding rapidly, and I foresee more purchases becoming a part of my regular Nostr experience soon enough.
-
I thought about including screenshots for this, but I would much rather you go check these clients out for yourself.
-
-
 @ 4961e68d:a2212e1c
2025-05-02 07:47:16
@ 4961e68d:a2212e1c
2025-05-02 07:47:16热死人了
-
 @ ecda4328:1278f072
2025-05-23 18:16:24
@ ecda4328:1278f072
2025-05-23 18:16:24And what does it mean to withdraw back to Bitcoin Layer 1?
Disclaimer: This post was written with help from ChatGPT-4o. If you spot any mistakes or have suggestions — feel free to reply or zap in feedback!
Let’s break it down — using three popular setups:
1. Wallet of Satoshi (WoS)
Custodial — you don’t touch Lightning directly
Sending sats:
- You open WoS, paste a Lightning invoice, hit send.
- WoS handles the payment entirely within their system.
- If recipient uses WoS: internal balance update.
- If external: routed via their node.
- You never open channels, construct routes, or sign anything.
Withdrawing to L1:
- You paste a Bitcoin address.
- WoS sends a regular on-chain transaction from their custodial wallet.
- You pay a fee. It’s like a bank withdrawal.
You don’t interact with Lightning directly. Think of it as a trusted 3rd party Lightning “bank”.
2. Phoenix Wallet
Non-custodial — you own keys, Phoenix handles channels
Sending sats:
- You scan a Lightning invoice and hit send.
- Phoenix uses its backend node (ACINQ) to route the payment.
- If needed, it opens a real 2-of-2 multisig channel on-chain automatically.
- You own your keys (12-word seed), Phoenix abstracts the technical parts.
Withdrawing to L1:
- You enter your Bitcoin address.
- Phoenix closes your Lightning channel (cooperatively, if possible).
- Your sats are sent as a real Bitcoin transaction to your address.
You’re using Lightning “for real,” with real Bitcoin channels — but Phoenix smooths out the UX.
3. Your Own Lightning Node
Self-hosted — you control everything
Sending sats:
- You manage your channels manually (or via automation).
- Your node:
- Reads the invoice
- Builds a route using HTLCs
- Sends the payment using conditional logic (preimages, time locks).
- If routing fails: retry or adjust liquidity.
Withdrawing to L1:
- You select and close a channel.
- A channel closing transaction is broadcast:
- Cooperative = fast and cheap
- Force-close = slower, more expensive, and time-locked
- Funds land in your on-chain wallet.
You have full sovereignty — but also full responsibility (liquidity, fees, backups, monitoring).
Core Tech Behind It: HTLCs, Multisig — and No Sidechain
- Lightning channels = 2-of-2 multisig Bitcoin addresses
- Payments = routed via HTLCs (Hashed Time-Locked Contracts)
- HTLCs are off-chain, but enforceable on-chain if needed
- Important:
- The Lightning Network is not a sidechain.
- It doesn't use its own token, consensus, or separate blockchain.
- Every Lightning channel is secured by real Bitcoin on L1.
Lightning = fast, private, off-chain Bitcoin — secured by Bitcoin itself.
Summary Table
| Wallet | Custody | Channel Handling | L1 Withdrawal | HTLC Visibility | User Effort | |--------------------|--------------|------------------------|---------------------|------------------|--------------| | Wallet of Satoshi | Custodial | None | Internal to external| Hidden | Easiest | | Phoenix Wallet | Non-custodial| Auto-managed real LN | Channel close | Abstracted | Low effort | | Own Node | You | Manual | Manual channel close| Full control | High effort |
Bonus: Withdrawing from LN to On-Chain
- WoS: sends sats from their wallet — like PayPal.
- Phoenix: closes a real channel and sends your UTXO on-chain.
- Own node: closes your multisig contract and broadcasts your pre-signed tx.
Bitcoin + Lightning = Sovereign money + Instant payments.
Choose the setup that fits your needs — and remember, you can always level up later.P.S. What happens in Lightning... usually stays in Lightning.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:48:04
@ 6d5c826a:4b27b659
2025-05-23 21:48:04- GNS3 - Graphical network simulator that provides a variety of virtual appliances. (Source Code)
GPL-3.0Python - OpenWISP - Open Source Network Management System for OpenWRT based routers and access points. (Demo, Source Code)
GPL-3.0Python - Oxidized - Network device configuration backup tool.
Apache-2.0Ruby - phpIPAM - Open source IP address management with PowerDNS integration. (Source Code)
GPL-3.0PHP - RANCID - Monitor network devices configuration and maintain history of changes. (Source Code)
BSD-3-ClausePerl/Shell - rConfig - Network device configuration management tool. (Source Code)
GPL-3.0PHP
- GNS3 - Graphical network simulator that provides a variety of virtual appliances. (Source Code)
-
 @ 866e0139:6a9334e5
2025-05-23 17:57:24
@ 866e0139:6a9334e5
2025-05-23 17:57:24Autor: Caitlin Johnstone. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Ich hörte einem jungen Autor zu, der eine Idee beschrieb, die ihn so sehr begeisterte, dass er die Nacht zuvor nicht schlafen konnte. Und ich erinnerte mich daran, wie ich mich früher – vor Gaza – über das Schreiben freuen konnte. Dieses Gefühl habe ich seit 2023 nicht mehr gespürt.
Ich beklage mich nicht und bemitleide mich auch nicht selbst, ich stelle einfach fest, wie unglaublich düster und finster die Welt in dieser schrecklichen Zeit geworden ist. Es wäre seltsam und ungesund, wenn ich in den letzten anderthalb Jahren Freude an meiner Arbeit gehabt hätte. Diese Dinge sollen sich nicht gut anfühlen. Nicht, wenn man wirklich hinschaut und ehrlich zu sich selbst ist in dem, was man sieht.
Es war die ganze Zeit über so hässlich und so verstörend. Es gibt eigentlich keinen Weg, all diesen Horror umzudeuten oder irgendwie erträglich zu machen. Alles, was man tun kann, ist, an sich selbst zu arbeiten, um genug inneren Raum zu schaffen, um die schlechten Gefühle zuzulassen und sie ganz durchzufühlen, bis sie sich ausgedrückt haben. Lass die Verzweiflung herein. Die Trauer. Die Wut. Den Schmerz. Lass sie deinen Körper vollständig durchfließen, ohne Widerstand, und steh dann auf und schreibe das nächste Stück.
Das ist es, was Schreiben für mich jetzt ist. Es ist nie etwas, worüber ich mich freue, es zu teilen, oder wofür ich von Inspiration erfüllt bin. Wenn überhaupt, dann fühlt es sich eher so an wie: „Okay, hier bitte, es tut mir schrecklich leid, dass ich euch das zeigen muss, Leute.“ Es ist das Starren in die Dunkelheit, in das Blut, in das Gemetzel, in die gequälten Gesichter – und das Aufschreiben dessen, was ich sehe, Tag für Tag.
Nichts daran ist angenehm oder befriedigend. Es ist einfach das, was man tut, wenn ein Genozid in Echtzeit vor den eigenen Augen stattfindet, mit der Unterstützung der eigenen Gesellschaft. Alles daran ist entsetzlich, und es gibt keinen Weg, das schönzureden – aber man tut, was getan werden muss. So, wie man es täte, wenn es die eigene Familie wäre, die da draußen im Schutt liegt.
Dieser Genozid hat mich für immer verändert. Er hat viele Menschen für immer verändert. Wir werden nie wieder dieselben sein. Die Welt wird nie wieder dieselbe sein. Ganz gleich, was passiert oder wie dieser Albtraum endet – die Dinge werden nie wieder so sein wie zuvor.
Und das sollten sie auch nicht. Der Holocaust von Gaza ist das Ergebnis der Welt, wie sie vor ihm war. Unsere Gesellschaft hat ihn hervorgebracht – und jetzt starrt er uns allen direkt ins Gesicht. Das sind wir. Das ist die Frucht des Baumes, den die westliche Zivilisation bis zu diesem Punkt gepflegt hat.
Jetzt geht es nur noch darum, alles zu tun, was wir können, um den Genozid zu beenden – und sicherzustellen, dass die Welt die richtigen Lehren daraus zieht. Das ist eines der würdigsten Anliegen, denen man sich in diesem Leben widmen kann.
Ich habe noch immer Hoffnung, dass wir eine gesunde Welt haben können. Ich habe noch immer Hoffnung, dass das Schreiben über das, was geschieht, eines Tages wieder Freude bereiten kann. Aber diese Dinge liegen auf der anderen Seite eines langen, schmerzhaften, konfrontierenden Weges, der in den kommenden Jahren vor uns liegt. Es gibt keinen Weg daran vorbei.
Die Welt kann keinen Frieden und kein Glück finden, solange wir uns nicht vollständig damit auseinandergesetzt haben, was wir Gaza angetan haben.
Dieser Text ist die deutsche Übersetzung dieses Substack-Artikels von Caitlin Johnstone.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 4961e68d:a2212e1c
2025-05-02 07:46:46
@ 4961e68d:a2212e1c
2025-05-02 07:46:46热死人了!
-
 @ 6d5c826a:4b27b659
2025-05-23 21:47:44
@ 6d5c826a:4b27b659
2025-05-23 21:47:44- Adagios - Web based Nagios interface for configuration and monitoring (replacement to the standard interface), and a REST interface. (Source Code)
AGPL-3.0Docker/Python - Alerta - Distributed, scalable and flexible monitoring system. (Source Code)
Apache-2.0Python - Beszel - Lightweight server monitoring platform that includes Docker statistics, historical data, and alert functions. (Source Code)
MITGo - Cacti - Web-based network monitoring and graphing tool. (Source Code)
GPL-2.0PHP - cadvisor - Analyzes resource usage and performance characteristics of running containers.
Apache-2.0Go - checkmk - Comprehensive solution for monitoring of applications, servers, and networks. (Source Code)
GPL-2.0Python/PHP - dashdot - A simple, modern server dashboard for smaller private servers. (Demo)
MITNodejs/Docker - EdMon - A command-line monitoring application helping you to check that your hosts and services are available, with notifications support.
MITJava - eZ Server Monitor - A lightweight and simple dashboard monitor for Linux, available in Web and Bash application. (Source Code)
GPL-3.0PHP/Shell - glances - Open-source, cross-platform real-time monitoring tool with CLI and web dashboard interfaces and many exporting options. (Source Code)
GPL-3.0Python - Healthchecks - Monitoring for cron jobs, background services and scheduled tasks. (Source Code)
BSD-3-ClausePython - Icinga - Nagios fork that has since lapped nagios several times. Comes with the possibility of clustered monitoring. (Source Code)
GPL-2.0C++ - LibreNMS - Fully featured network monitoring system that provides a wealth of features and device support. (Source Code)
GPL-3.0PHP - Linux Dash - A low-overhead monitoring web dashboard for a GNU/Linux machine.
MITNodejs/Go/Python/PHP - Monit - Small utility for managing and monitoring Unix systems. (Source Code)
AGPL-3.0C - Munin - Networked resource monitoring tool. (Source Code)
GPL-2.0Perl/Shell - Naemon - Network monitoring tool based on the Nagios 4 core with performance enhancements and new features. (Source Code)
GPL-2.0C - Nagios - Computer system, network and infrastructure monitoring software application. (Source Code)
GPL-2.0C - Netdata - Distributed, real-time, performance and health monitoring for systems and applications. Runs on Linux, FreeBSD, and MacOS. (Source Code)
GPL-3.0C - NetXMS - Open Source network and infrastructure monitoring and management. (Source Code)
LGPL-3.0/GPL-3.0Java/C++/C - Observium Community Edition - Network monitoring and management platform that provides real-time insight into network health and performance.
QPL-1.0PHP - openITCOCKPIT Community Edition - Monitoring Suite featuring seamless integrations with Naemon, Checkmk, Grafana and more. (Demo, Source Code)
GPL-3.0deb/Docker - Performance Co-Pilot - Lightweight, distributed system performance and analysis framework. (Source Code)
LGPL-2.1/GPL-2.0C - PHP Server Monitor - Open source tool to monitor your servers and websites. (Source Code)
GPL-3.0PHP - PhpSysInfo - A customizable PHP script that displays information about your system nicely. (Source Code)
GPL-2.0PHP - Prometheus - Service monitoring system and time series database. (Source Code)
Apache-2.0Go - Riemann - Flexible and fast events processor allowing complex events/metrics analysis. (Source Code)
EPL-1.0Java - rtop - Interactive, remote system monitoring tool based on SSH.
MITGo - ruptime - Classic system status server.
AGPL-3.0Shell - Scrutiny - Web UI for hard drive S.M.A.R.T monitoring, historical trends & real-world failure thresholds.
MITGo - Sensu - Monitoring tool for ephemeral infrastructure and distributed applications. (Source Code)
MITGo - Status - Simple and lightweight system monitoring tool for small homeservers with a pleasant web interface. (Demo
MITPython - Thruk - Multibackend monitoring web interface with support for Naemon, Nagios, Icinga and Shinken. (Source Code)
GPL-1.0Perl - Wazuh - Unified XDR and SIEM protection for endpoints and cloud workloads. (Source Code)
GPL-2.0C - Zabbix - Enterprise-class software for monitoring of networks and applications. (Source Code)
GPL-2.0C
- Adagios - Web based Nagios interface for configuration and monitoring (replacement to the standard interface), and a REST interface. (Source Code)
-
 @ 91bea5cd:1df4451c
2025-05-23 17:04:49
@ 91bea5cd:1df4451c
2025-05-23 17:04:49Em nota, a prefeitura justificou que essas alterações visam ampliar a segurança das praias, conforto e organização, para os frequentadores e trabalhadores dos locais. No entanto, Orla Rio, concessionária responsável pelos espaços, e o SindRio, sindicato de bares e restaurantes, ficou insatisfeita com as medidas e reforçou que a música ao vivo aumenta em mais de 10% o ticket médio dos estabelecimentos e contribui para manter os empregos, especialmente na baixa temporada.
De acordo com Paes, as medidas visam impedir práticas ilegais para que a orla carioca continue sendo um espaço ativo econômico da cidade: “Certas práticas são inaceitáveis, especialmente por quem tem autorização municipal. Vamos ser mais restritivos e duros. A orla é de todos”.
Saiba quais serão as 16 proibições nas praias do Rio de Janeiro
- Utilização de caixas de som, instrumentos musicais, grupos ou qualquer equipamento sonoro, em qualquer horário. Apenas eventos autorizados terão permissão.
- Venda ou distribuição de bebidas em garrafas de vidro em qualquer ponto da areia ou do calçadão.
- Estruturas comerciais ambulantes sem autorização, como carrocinhas, trailers, food trucks e barracas.
- Comércio ambulante sem permissão, incluindo alimentos em palitos, churrasqueiras, isopores ou bandejas térmicas improvisadas.
- Circulação de ciclomotores e patinetes motorizados no calçadão.
- Escolinhas de esportes ou recreações não autorizadas pelo poder público municipal.
- Ocupação de área pública com estruturas fixas ou móveis de grandes proporções sem autorização.
- Instalação de acampamentos improvisados em qualquer trecho da orla.
- Práticas de comércio abusivo ou enganosas, incluindo abordagens insistentes. Quiosques e barracas devem exibir cardápio, preços e taxas de forma clara.
- Uso de animais para entretenimento, transporte ou comércio.
- Hasteamento ou exibição de bandeiras em mastros ou suportes.
- Fixação de objetos ou amarras em árvores ou vegetação.
- Cercadinhos feitos por ambulantes ou quiosques, que impeçam a livre circulação de pessoas.
- Permanência de carrinhos de transporte de mercadorias ou equipamentos fora dos momentos de carga e descarga.
- Armazenamento de produtos, barracas ou equipamentos enterrados na areia ou depositados na vegetação de restinga.
- Uso de nomes, marcas, logotipos ou slogans em barracas. Apenas a numeração sequencial da prefeitura será permitida.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:47:22
@ 6d5c826a:4b27b659
2025-05-23 21:47:22- Chocolatey - The package manager for Windows. (Source Code)
Apache-2.0C#/PowerShell - Clonezilla - Partition and disk imaging/cloning program. (Source Code)
GPL-2.0Perl/Shell/Other - DadaMail - Mailing List Manager, written in Perl. (Source Code)
GPL-2.0Perl - Fog - Cloning/imaging solution/rescue suite. (Source Code)
GPL-3.0PHP/Shell - phpList - Newsletter and email marketing software. (Source Code)
AGPL-3.0PHP
- Chocolatey - The package manager for Windows. (Source Code)
-
 @ c1e9ab3a:9cb56b43
2025-05-01 17:29:18
@ c1e9ab3a:9cb56b43
2025-05-01 17:29:18High-Level Overview
Bitcoin developers are currently debating a proposed change to how Bitcoin Core handles the
OP_RETURNopcode — a mechanism that allows users to insert small amounts of data into the blockchain. Specifically, the controversy revolves around removing built-in filters that limit how much data can be stored using this feature (currently capped at 80 bytes).Summary of Both Sides
Position A: Remove OP_RETURN Filters
Advocates: nostr:npub1ej493cmun8y9h3082spg5uvt63jgtewneve526g7e2urca2afrxqm3ndrm, nostr:npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vg, nostr:npub17u5dneh8qjp43ecfxr6u5e9sjamsmxyuekrg2nlxrrk6nj9rsyrqywt4tp, others
Arguments: - Ineffectiveness of filters: Filters are easily bypassed and do not stop spam effectively. - Code simplification: Removing arbitrary limits reduces code complexity. - Permissionless innovation: Enables new use cases like cross-chain bridges and timestamping without protocol-level barriers. - Economic regulation: Fees should determine what data gets added to the blockchain, not protocol rules.
Position B: Keep OP_RETURN Filters
Advocates: nostr:npub1lh273a4wpkup00stw8dzqjvvrqrfdrv2v3v4t8pynuezlfe5vjnsnaa9nk, nostr:npub1s33sw6y2p8kpz2t8avz5feu2n6yvfr6swykrnm2frletd7spnt5qew252p, nostr:npub1wnlu28xrq9gv77dkevck6ws4euej4v568rlvn66gf2c428tdrptqq3n3wr, others
Arguments: - Historical intent: Satoshi included filters to keep Bitcoin focused on monetary transactions. - Resource protection: Helps prevent blockchain bloat and abuse from non-financial uses. - Network preservation: Protects the network from being overwhelmed by low-value or malicious data. - Social governance: Maintains conservative changes to ensure long-term robustness.
Strengths and Weaknesses
Strengths of Removing Filters
- Encourages decentralized innovation.
- Simplifies development and maintenance.
- Maintains ideological purity of a permissionless system.
Weaknesses of Removing Filters
- Opens the door to increased non-financial data and potential spam.
- May dilute Bitcoin’s core purpose as sound money.
- Risks short-term exploitation before economic filters adapt.
Strengths of Keeping Filters
- Preserves Bitcoin’s identity and original purpose.
- Provides a simple protective mechanism against abuse.
- Aligns with conservative development philosophy of Bitcoin Core.
Weaknesses of Keeping Filters
- Encourages central decision-making on allowed use cases.
- Leads to workarounds that may be less efficient or obscure.
- Discourages novel but legitimate applications.
Long-Term Consequences
If Filters Are Removed
- Positive: Potential boom in new applications, better interoperability, cleaner architecture.
- Negative: Risk of increased blockchain size, more bandwidth/storage costs, spam wars.
If Filters Are Retained
- Positive: Preserves monetary focus and operational discipline.
- Negative: Alienates developers seeking broader use cases, may ossify the protocol.
Conclusion
The debate highlights a core philosophical split in Bitcoin: whether it should remain a narrow monetary system or evolve into a broader data layer for decentralized applications. Both paths carry risks and tradeoffs. The outcome will shape not just Bitcoin's technical direction but its social contract and future role in the broader crypto ecosystem.
-
 @ 866e0139:6a9334e5
2025-04-30 17:55:13
@ 866e0139:6a9334e5
2025-04-30 17:55:13Autor: Ulrike Guérot. (Foto: Manuela Haltiner). Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
https://www.youtube.com/watch?v=KarwcXKmD3E
Liebe Freunde und Bekannte,
liebe Friedensbewegte,
liebe Dresdener, Dresden ist ja auch eine kriegsgeplagte Stadt,
dies ist meine dritte Rede auf einer Friedensdemonstration innerhalb von nur gut einem halben Jahr: München im September, München im Februar, Dresden im April. Und der Krieg rückt immer näher! Wer sich den „Operationsplan Deutschland über die zivil-militärische Kooperation als wesentlicher Bestandteil der Kriegsführung“ anschaut, dem kann nur schlecht werden zu sehen, wie weit die Kriegsvorbereitungen schon gediehen sind.
Doch bevor ich darauf eingehe, möchte ich mich als erstes distanzieren von dem wieder einmal erbärmlichen Framing dieser Demo als Querfront oder Schwurblerdemo. Durch dieses Framing wurde diese Demo vom Dresdener Marktplatz auf den Postplatz verwiesen, wurden wir geschmäht und wurde die Stadtverwaltung Dresden dazu gebracht, eine „genehmere“ Demo auf dem Marktplatz zuzulassen! Es wäre schön, wenn wir alle - alle! - solche Framings weglassen würden und uns als Friedensbewegte die Hand reichen! Der Frieden im eigenen Haus ist die Voraussetzung für unsere Friedensarbeit. Der Streit in unserem Haus nutzt nur denen, die den Krieg wollen und uns spalten!
Ich möchte hier noch einmal klarstellen, von welcher Position aus ich hier und heute wiederholt auf einer Bühne spreche: Ich spreche als engagierte Bürgerin der Bundesrepublik Deutschland. Ich spreche als Europäerin, die lange Jahre in und an dem einstigen Friedensprojekt EU gearbeitet hat. Ich spreche als Enkelin von zwei Großvätern. Der eine ist im Krieg gefallen, der andere kam ohne Beine zurück. Ich spreche als Tochter einer Mutter, die 1945, als 6-Jährige, unter traumatischen Umständen aus Schlesien vertrieben wurde, nach Delitzsch in Sachsen übrigens. Ich spreche als Mutter von zwei Söhnen, 33 und 31 Jahre, von denen ich nicht möchte, dass sie in einen Krieg müssen. Von dieser, und nur dieser Position aus spreche ich heute zu Ihnen und von keiner anderen! Ich bin nicht rechts, ich bin keine Schwurblerin, ich bin nicht radikal, ich bin keine Querfront.
Als Bürgerin wünsche ich mir – nein, verlange ich! – dass die Bundesrepublik Deutschland sich an ihre gesetzlichen Grundlagen und Vertragstexte hält. Das sind namentlich: Die Friedensklausel des Grundgesetzes aus Art. 125 und 126 GG, dass von deutschem Boden nie wieder Krieg ausgeht. Und der Zwei-plus-Vier-Vertrag, in dem Deutschland 1990 unterschrieben hat, dass es nie an einem bewaffneten Konflikt gegen Russland teilnimmt. Ich schäme mich dafür, dass mein Land dabei ist, vertragsbrüchig zu werden. Ich bitte Friedrich Merz, den designierten Bundeskanzler, keinen Vertragsbruch durch die Lieferung von Taurus-Raketen zu begehen!
Ich bitte ferner darum, dass sich dieses Land an seine didaktischen Vorgaben für Schulen hält, die im immer noch geltenden „Beutelsbacher Konsens“ aus den 1970er Jahren festgelegt wurden. In diesem steht in Artikel I. ein Überwältigungsverbot: „Es ist nicht erlaubt, den Schüler – mit welchen Mitteln auch immer – im Sinne erwünschter Meinungen zu überrumpeln und damit an der Gewinnung eines selbständigen Urteils zu hindern.“ Vor diesem Hintergrund ist es nicht erlaubt, Soldaten oder Gefreite in Schulen zu schicken und für die Bundeswehr zu werben. Vielmehr wäre es geboten, unsere Kinder über Art. 125 & 126 GG und die Friedenspflicht des Landes und seine Geschichte mit Blick auf Russland aufzuklären.
Als Europäerin wünsche ich mir, dass wir die europäische Hymne, Beethovens 9. Sinfonie, ernst nehmen, deren Text da lautet: Alle Menschen werden Brüder. Alle Menschen werden Brüder. Alle! Dazu gehören auch die Russen und natürlich auch die Ukrainer!
Als Europäerin, die in den 1990er Jahren für den großartigen EU-Kommissionspräsidenten Jacques Delors gearbeitet hat, Katholik, Sozialist und Gewerkschafter, wünsche ich mir, dass wir das Versprechen, #Europa ist nie wieder Krieg, ernst nehmen. Wir haben es 70 Jahre lang auf diesem Kontinent erzählt. Die Lügen und die Propaganda, mit der jetzt die Kriegsnotwendigkeit gegen Russland herbeigeredet wird, sind unerträglich. Die EU, Friedensnobelpreisträgerin von 2012, ist dabei – oder hat schon – ihr Ansehen in der Welt verloren. Es ist eine politische Tragödie! Neben ihrem Ansehen ist die EU jetzt dabei, das zivilisatorische Erbe Europas zu verspielen, die civilité européenne, wie der französische Historiker und Marxist, Étienne Balibar es nennt.
Ein Element dieses historischen Erbes ist es, dass uns in Europa eint, dass wir über Jahrhunderte alle zugleich Täter und Opfer gewesen sind. Ce que nous partageons, c’est ce que nous étions tous bourreaux et victimes. So schreibt es der französische Literat Laurent Gaudet in seinem europäischen Epos, L’Europe. Une Banquet des Peuples von 2016.
Das heißt, dass niemand in Europa, niemand – auch die Esten nicht! – das Recht hat, vorgängige Traumata, die die baltischen Staaten unbestrittenermaßen mit Stalin-Russland gehabt haben, zu verabsolutieren, auf die gesamte EU zu übertragen, die EU damit zu blockieren und die Politikgestaltung der EU einseitig auf einen Kriegskurs gegen Russland auszurichten. Ich wende mich mit dieser Feststellung direkt an Kaja Kalles, die Hohe Beauftragte für Sicherheits- und Außenpolitik der EU und hoffe, dass sie diese Rede hört und das Epos von Laurent Gaudet liest.
Es gibt keinen gerechten Krieg! Krieg ist immer nur Leid. In Straßburg, dem Sitz des Europäischen Parlaments, steht auf dem Place de la République eine Statue, eine Frau, die Republik. Sie hält in jedem Arm einen Sohn, einen Elsässer und einen Franzosen, die aus dem Krieg kommen. In der Darstellung der Bronzefigur haben die beiden Soldaten-Männer ihre Uniformen schon ausgezogen und werden von Madame la République gehalten und getröstet. An diesem Denkmal sollten sich alle Abgeordnete des Straßburger Europaparlamentes am 9. Mai versammeln. Ich zitiere noch einmal Cicero: Der ungerechteste Friede ist besser als der gerechteste Krieg. Für den Vortrag dieses Zitats eines der größten Staatsdenker des antiken Roms in einer Fernsehsendung bin ich 2022 mit einem Shitstorm überzogen worden. Allein das ist Ausdruck des Verfalls unserer Diskussionskultur in unfassbarem Ausmaß, ganz besonders in Deutschland.
Als Europäerin verlange ich die Überwindung unserer kognitiven Dissonanz. Wenn schon die New York Times am 27. März 2025 ein 27-seitiges Dossier veröffentlicht, das nicht nur belegt, was man eigentlich schon weiß, aber bisher nicht sagen durfte, nämlich, dass der ukrainisch-russische Krieg ein eindeutiger Stellvertreter-Krieg der USA ist, in der die Ukraine auf monströseste Weise instrumentalisiert wurde – was das Dossier der NYT unumwunden zugibt! – wäre es an der Zeit, die eindeutige Schuldzuweisung an Russland für den Krieg zurückzuziehen und die gezielt verbreitete Russophobie in Europa zu beenden. Anstatt dass – wofür es leider viele Verdachtsmomente gibt – die EU die Friedensverhandlungen in Saudi-Arabien nach Strich und Faden torpediert.
Der französische Philosoph Luc Ferry hat vor ein paar Tagen im prime time französischen Fernsehen ganz klar gesagt, dass der Krieg 2014 nach der Instrumentalisierung des Maidan durch die USA von der West-Ukraine ausging, dass Zelensky diesen Krieg wollte und – mit amerikanischer Rückendeckung – provoziert hat, dass Putin nicht Hitler ist und dass die einzigen mit faschistoiden Tendenzen in der ukrainischen Regierung sitzen. Ich wünschte mir, ein solches Statement wäre auch im Deutschen Fernsehen möglich und danke Richard David Precht, dass er, der noch in den Öffentlich-Rechtlichen Rundfunk vorgelassen wird, an dieser Stelle versucht, etwas Vernunft in die Debatte zu bringen.
Auch ist es gerade als Europäerin nicht hinzunehmen, dass russische Diplomaten von den Feierlichkeiten am 8. Mai 2025 ausgeschlossen werden sollen, ausgerechnet 80 Jahre nach Ende des II. Weltkrieges. Nicht nur sind Feierlichkeiten genau dazu da, sich die Hand zu reichen und den Frieden zu feiern. Doch gerade vor dem Hintergrund von 27 Millionen gefallenen sowjetischen Soldaten ist die Zurückweisung der Russen von den Feierlichkeiten geradezu eklatante Geschichtsvergessenheit.
***
Der Völkerbund hat 1925 die Frage erörtert, warum der I. Weltkrieg noch so lange gedauert hat, obgleich er militärisch bereits 1916 nach Eröffnung des Zweifrontenkrieges zu Lasten des Deutschen Reiches entschieden war. Wir erinnern uns: Für die Niederlage wurden mit der Dolchstoßlegende die jüdischen, kommunistischen und sozialistischen Pazifisten verantwortlich gemacht. Richtig ist, so der Bericht des Völkerbundes von 1925, dass allein die Rüstungsindustrie dafür gesorgt hat, dass der militärisch eigentlich schon entschiedene Krieg noch zwei weitere Jahre als Materialabnutzungs- und Stellungskrieg weiterbetrieben wurde, nur, damit noch ein bisschen Geld verdient werden konnte. Genauso scheint es heute zu sein. Der Krieg ist militärisch entschieden. Er kann und muss sofort beendet werden, und das passiert lediglich deswegen nicht, weil der Westen seine Niederlage nicht zugeben kann. Hochmut aber kommt vor dem Fall, und es darf nicht sein, dass für europäischen Hochmut jeden Tag rund 2000 ukrainische oder russische Soldaten und viele Zivilisten sterben. Die offenbare europäische Absicht, den Krieg jetzt einzufrieren, nur, um ihn 2029/ 2030 wieder zu entfachen, wenn Europa dann besser aufgerüstet ist, ist nur noch zynisch.
Als Kriegsenkelin von Kriegsversehrten, Tochter einer Flüchtlingsmutter und Mutter von zwei Söhnen, deren französischer Urgroßvater 6 Jahre in deutscher Kriegsgefangenschaft war, wünsche ich mir schließlich und zum Abschluss, dass wir die Kraft haben werden, wenn dieser Wahnsinn, den man den europäischen Bürgern gerade aufbürdet, vorbei sein wird, ein neues europäisches Projekt zu erdenken und zu erbauen, in dem Europa politisch geeint ist und es bleibt, aber dezentral, regional, subsidiär, friedlich und neutral gestaltet wird. Also ein Europa jenseits der Strukturen der EU, das bereit ist, die Pax Americana zu überwinden, aus der NATO auszutreten und der multipolaren Welt seine Hand auszustrecken! Unser Europa ist postimperial, postkolonial, groß, vielfältig und friedfertig!
Ulrike Guérot, Jg. 1964, ist europäische Professorin, Publizistin und Bestsellerautorin. Seit rund 30 Jahren beschäftigt sie sich in europäischen Think Tanks und Universitäten in Paris, Brüssel, London, Washington, New York, Wien und Berlin mit Fragen der europäischen Demokratie sowie mit der Rolle Europas in der Welt. Ulrike Guérot ist seit März 2014 Gründerin und Direktorin des European Democracy Lab e.V., Berlin und initiierte im März 2023 das European Citizens Radio, das auf Spotify zu finden ist. Zuletzt erschien von ihr „Über Halford J. Mackinders Heartland-Theorie, Der geografische Drehpunkt der Geschichte“ (Westend, 2024). Mehr Infos zur Autorin hier.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:47:03
@ 6d5c826a:4b27b659
2025-05-23 21:47:03- Beats - Single-purpose data shippers that send data from hundreds or thousands of machines and systems to Logstash or Elasticsearch. (Source Code)
Apache-2.0Go - Collectd - System statistics collection daemon. (Source Code)
MITC - Diamond - Daemon that collects system metrics and publishes them to Graphite (and others).
MITPython - Grafana - A Graphite & InfluxDB Dashboard and Graph Editor. (Source Code)
AGPL-3.0Go - Graphite - Scalable graphing server. (Source Code)
Apache-2.0Python - RRDtool - Industry standard, high performance data logging and graphing system for time series data. (Source Code)
GPL-2.0C - Statsd - Daemon that listens for statistics like counters and timers, sent over UDP or TCP, and sends aggregates to one or more pluggable backend services.
MITNodejs - tcollector - Gathers data from local collectors and pushes the data to OpenTSDB. (Source Code)
LGPL-3.0/GPL-3.0Python - Telegraf - Plugin-driven server agent for collecting, processing, aggregating, and writing metrics.
MITGo
- Beats - Single-purpose data shippers that send data from hundreds or thousands of machines and systems to Logstash or Elasticsearch. (Source Code)
-
 @ 5144fe88:9587d5af
2025-05-23 17:01:37
@ 5144fe88:9587d5af
2025-05-23 17:01:37The recent anomalies in the financial market and the frequent occurrence of world trade wars and hot wars have caused the world's political and economic landscape to fluctuate violently. It always feels like the financial crisis is getting closer and closer.
This is a systematic analysis of the possibility of the current global financial crisis by Manus based on Ray Dalio's latest views, US and Japanese economic and financial data, Buffett's investment behavior, and historical financial crises.
Research shows that the current financial system has many preconditions for a crisis, especially debt levels, market valuations, and investor behavior, which show obvious crisis signals. The probability of a financial crisis in the short term (within 6-12 months) is 30%-40%,
in the medium term (within 1-2 years) is 50%-60%,
in the long term (within 2-3 years) is 60%-70%.
Japan's role as the world's largest holder of overseas assets and the largest creditor of the United States is particularly critical. The sharp appreciation of the yen may be a signal of the return of global safe-haven funds, which will become an important precursor to the outbreak of a financial crisis.
Potential conditions for triggering a financial crisis Conditions that have been met 1. High debt levels: The debt-to-GDP ratio of the United States and Japan has reached a record high. 2. Market overvaluation: The ratio of stock market to GDP hits a record high 3. Abnormal investor behavior: Buffett's cash holdings hit a record high, with net selling for 10 consecutive quarters 4. Monetary policy shift: Japan ends negative interest rates, and the Fed ends the rate hike cycle 5. Market concentration is too high: a few technology stocks dominate market performance
Potential trigger points 1. The Bank of Japan further tightens monetary policy, leading to a sharp appreciation of the yen and the return of overseas funds 2. The US debt crisis worsens, and the proportion of interest expenses continues to rise to unsustainable levels 3. The bursting of the technology bubble leads to a collapse in market confidence 4. The trade war further escalates, disrupting global supply chains and economic growth 5. Japan, as the largest creditor of the United States, reduces its holdings of US debt, causing US debt yields to soar
Analysis of the similarities and differences between the current economic environment and the historical financial crisis Debt level comparison Current debt situation • US government debt to GDP ratio: 124.0% (December 2024) • Japanese government debt to GDP ratio: 216.2% (December 2024), historical high 225.8% (March 2021) • US total debt: 36.21 trillion US dollars (May 2025) • Japanese debt/GDP ratio: more than 250%-263% (Japanese Prime Minister’s statement)
Before the 2008 financial crisis • US government debt to GDP ratio: about 64% (2007) • Japanese government debt to GDP ratio: about 175% (2007)
Before the Internet bubble in 2000 • US government debt to GDP ratio: about 55% (1999) • Japanese government debt to GDP ratio: about 130% (1999)
Key differences • The current US debt-to-GDP ratio is nearly twice that before the 2008 crisis • The current Japanese debt-to-GDP ratio is more than 1.2 times that before the 2008 crisis • Global debt levels are generally higher than historical pre-crisis levels • US interest payments are expected to devour 30% of fiscal revenue (Moody's warning)
Monetary policy and interest rate environment
Current situation • US 10-year Treasury yield: about 4.6% (May 2025) • Bank of Japan policy: end negative interest rates and start a rate hike cycle • Bank of Japan's holdings of government bonds: 52%, plans to reduce purchases to 3 trillion yen per month by January-March 2026 • Fed policy: end the rate hike cycle and prepare to cut interest rates
Before the 2008 financial crisis • US 10-year Treasury yield: about 4.5%-5% (2007) • Fed policy: continuous rate hikes from 2004 to 2006, and rate cuts began in 2007 • Bank of Japan policy: maintain ultra-low interest rates
Key differences • Current US interest rates are similar to those before the 2008 crisis, but debt levels are much higher than then • Japan is in the early stages of ending its loose monetary policy, unlike before historical crises • The size of global central bank balance sheets is far greater than at any time in history
Market valuations and investor behavior Current situation • The ratio of stock market value to the size of the US economy: a record high • Buffett's cash holdings: $347 billion (28% of assets), a record high • Market concentration: US stock growth mainly relies on a few technology giants • Investor sentiment: Technology stocks are enthusiastic, but institutional investors are beginning to be cautious
Before the 2008 financial crisis • Buffett's cash holdings: 25% of assets (2005) • Market concentration: Financial and real estate-related stocks performed strongly • Investor sentiment: The real estate market was overheated and subprime products were widely popular
Before the 2000 Internet bubble • Buffett's cash holdings: increased from 1% to 13% (1998) • Market concentration: Internet stocks were extremely highly valued • Investor sentiment: Tech stocks are in a frenzy
Key differences • Buffett's current cash holdings exceed any pre-crisis level in history • Market valuation indicators have reached a record high, exceeding the levels before the 2000 bubble and the 2008 crisis • The current market concentration is higher than any period in history, and a few technology stocks dominate market performance
Safe-haven fund flows and international relations Current situation • The status of the yen: As a safe-haven currency, the appreciation of the yen may indicate a rise in global risk aversion • Trade relations: The United States has imposed tariffs on Japan, which is expected to reduce Japan's GDP growth by 0.3 percentage points in fiscal 2025 • International debt: Japan is one of the largest creditors of the United States
Before historical crises • Before the 2008 crisis: International capital flows to US real estate and financial products • Before the 2000 bubble: International capital flows to US technology stocks
Key differences • Current trade frictions have intensified and the trend of globalization has weakened • Japan's role as the world's largest holder of overseas assets has become more prominent • International debt dependence is higher than any period in history
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 6d5c826a:4b27b659
2025-05-23 21:46:46
@ 6d5c826a:4b27b659
2025-05-23 21:46:46- aerc - Terminal MUA with a focus on plaintext and features for developers. (Source Code)
MITGo - Claws Mail - Old school email client (and news reader), based on GTK+. (Source Code)
GPL-3.0C - ImapSync - Simple IMAP migration tool for copying mailboxes to other servers. (Source Code)
NLPLPerl - Mutt - Small but very powerful text-based mail client. (Source Code)
GPL-2.0C - Sylpheed - Still developed predecessor to Claws Mail, lightweight mail client. (Source Code)
GPL-2.0C - Thunderbird - Free email application that's easy to set up and customize. (Source Code)
MPL-2.0C/C++
- aerc - Terminal MUA with a focus on plaintext and features for developers. (Source Code)
-
 @ cae03c48:2a7d6671
2025-05-23 16:01:05
@ cae03c48:2a7d6671
2025-05-23 16:01:05Bitcoin Magazine
Spark Partners with Breez to Launch Bitcoin-Native SDK for Lightning PaymentsToday, Breez and Spark have announced a new implementation of the Breez SDK, built on Spark’s Bitcoin-native Layer 2 infrastructure. According to a press release sent to Bitcoin Magazine, the update is intended to make it easier for developers to integrate self-custodial Bitcoin Lightning payments into everyday apps and services.
Few companies are as good as @Breez_Tech at putting Bitcoin in people’s hands. We’re incredibly humbled to have them building on Spark.
Learn more → https://t.co/KRPpWJa3os pic.twitter.com/QiCfHbWu9d
— Spark (@buildonspark) May 22, 2025
“This is what the future of Bitcoin looks like — fast, open, and embedded in the apps people use every day. By teaming up with Breez, we’re expanding the ecosystem and giving developers powerful, Bitcoin-native tools to build next-generation payment experiences. Together, we’re building the standard for global, peer-to-peer transactions,” said the creator of Spark Kevin Hurley.
The SDK supports LNURL, Lightning addresses, real-time mobile notifications, and includes bindings for all major programming languages and frameworks. It is designed to allow developers to build directly on Bitcoin without relying on bridges or external consensus. This collaboration gives developers tools to add Bitcoin payment features to apps used for monetization social apps, cross-border remittances, and in-game currencies.
“We need developers to bring Bitcoin into apps people use every day,” said the CEO of Breez Roy Sheinfeld. “That’s why we built the Breez SDK. We’re excited to build on Spark’s revolutionary architecture — giving developers a powerful new Bitcoin-native option and continuing to strengthen Lightning as the common language of Bitcoin.”
Breez will also operate as a Spark Service Provider (SSP), alongside Lightspark, to help support payment facilitation and the growth of Spark’s ecosystem. The new implementation is expected to be released later this year.
“We’re excited to see what developers build with Spark; it’s very exciting to see this come to the world,” said the co-founder and CEO of Lightspark David Marcus.
The Breez SDK is expanding

We’re joining forces with @buildonspark to release a new nodeless implementation of the Breez SDK — giving developers the tools they need to bring Bitcoin payments to everyday apps.
Bitcoin-Native
Powered by Spark’s…— Breez
 (@Breez_Tech) May 22, 2025
(@Breez_Tech) May 22, 2025Yesterday, Magic Eden also partnered with Spark to improve Bitcoin trading by addressing issues like slow transaction times, high fees, and poor user experience. The integration will introduce a native settlement system aimed at making transactions faster and more cost-effective, without using bridges or synthetic assets.
“We’re proud to be betting on BTC DeFi,” said the CEO of Magic Eden Jack Lu. “We’re going to lead the forefront of all Bitcoin DeFi to make BTC fast, fun, and for everyone with Magic Eden as the #1 BTC native app on-chain.”
This post Spark Partners with Breez to Launch Bitcoin-Native SDK for Lightning Payments first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:46:28
@ 6d5c826a:4b27b659
2025-05-23 21:46:28- Fluentd - Data collector for unified logging layer. (Source Code)
Apache-2.0Ruby - Flume - Distributed, reliable, and available service for efficiently collecting, aggregating, and moving large amounts of log data. (Source Code)
Apache-2.0Java - GoAccess - Real-time web log analyzer and interactive viewer that runs in a terminal or through the browser. (Source Code)
MITC - Loki - Log aggregation system designed to store and query logs from all your applications and infrastructure. (Source Code)
AGPL-3.0Go - rsyslog - Rocket-fast system for log processing. (Source Code)
GPL-3.0C
- Fluentd - Data collector for unified logging layer. (Source Code)
-
 @ 90152b7f:04e57401
2025-05-23 15:48:58
@ 90152b7f:04e57401
2025-05-23 15:48:58U.S. troops would enforce peace under Army study
The Washington Times - September 10, 2001
by Rowan Scarborough
https://www.ord.io/70787305 (image) https://www.ord.io/74522515 (text)
An elite U.S. Army study center has devised a plan for enforcing a major Israeli-Palestinian peace accord that would require about 20,000 well-armed troops stationed throughout Israel and a newly created Palestinian state. There are no plans by the Bush administration to put American soldiers into the Middle East to police an agreement forged by the longtime warring parties. In fact, Defense Secretary Donald H. Rumsfeld is searching for ways to reduce U.S. peacekeeping efforts abroad, rather than increasing such missions. But a 68-page paper by the Army School of Advanced Military Studies (SAMS) does provide a look at the daunting task any international peacekeeping force would face if the United Nations authorized it, and Israel and the Palestinians ever reached a peace agreement.
Located at Fort Leavenworth, Kan., the School for Advanced Military Studies is both a training ground and a think tank for some of the Army’s brightest officers. Officials say the Army chief of staff, and sometimes the Joint Chiefs of Staff, ask SAMS to develop contingency plans for future military operations. During the 1991 Persian Gulf war, SAMS personnel helped plan the coalition ground attack that avoided a strike up the middle of Iraqi positions and instead executed a “left hook” that routed the enemy in 100 hours.
The cover page for the recent SAMS project said it was done for the Joint Chiefs of Staff. But Maj. Chris Garver, a Fort Leavenworth spokesman, said the study was not requested by Washington. “This was just an academic exercise,” said Maj. Garver. “They were trying to take a current situation and get some training out of it.” The exercise was done by 60 officers dubbed “Jedi Knights,” as all second-year SAMS students are nicknamed.
The SAMS paper attempts to predict events in the first year of a peace-enforcement operation, and sees possible dangers for U.S. troops from both sides. It calls Israel’s armed forces a “500-pound gorilla in Israel. Well armed and trained. Operates in both Gaza . Known to disregard international law to accomplish mission. Very unlikely to fire on American forces. Fratricide a concern especially in air space management.”
Of the Mossad, the Israeli intelligence service, the SAMS officers say: “Wildcard. Ruthless and cunning. Has capability to target U.S. forces and make it look like a Palestinian/Arab act.”
On the Palestinian side, the paper describes their youth as “loose cannons; under no control, sometimes violent.” The study lists five Arab terrorist groups that could target American troops for assassination and hostage-taking. The study recommends “neutrality in word and deed” as one way to protect U.S. soldiers from any attack. It also says Syria, Egypt and Jordan must be warned “we will act decisively in response to external attack.”
It is unlikely either of the three would mount an attack. Of Syria’s military, the report says: “Syrian army quantitatively larger than Israeli Defense Forces, but largely seen as qualitatively inferior. More likely, however, Syrians would provide financial and political support to the Palestinians, as well as increase covert support to terrorism acts through Lebanon.” Of Egypt’s military, the paper says, “Egyptians also maintain a large army but have little to gain by attacking Israel.”
The plan does not specify a full order of battle. An Army source who reviewed the SAMS work said each of a possible three brigades would require about 100 Bradley fighting vehicles, 25 tanks, 12 self-propelled howitzers, Apache attack helicopters, Kiowa Warrior reconnaissance helicopters and Predator spy drones. The report predicts that nonlethal weapons would be used to quell unrest. U.S. European Command, which is headed by NATO’s supreme allied commander, would oversee the peacekeeping operation. Commanders would maintain areas of operation, or AOs, around Nablus, Jerusalem, Hebron and the Gaza strip. The study sets out a list of goals for U.S. troops to accomplish in the first 30 days. They include: “create conditions for development of Palestinian State and security of “; ensure “equal distribution of contract value or equivalent aid” that would help legitimize the peacekeeping force and stimulate economic growth; “promote U.S. investment in Palestine”; “encourage reconciliation between entities based on acceptance of new national identities”; and “build lasting relationship based on new legal borders and not religious-territorial claims.”
Maj. Garver said the officers who completed the exercise will hold major planning jobs once they graduate. “There is an application process” for students, he said. “They screen their records, and there are several tests they go through before they are accepted by the program. The bright planners of the future come out of this program.”
James Phillips, a Middle East analyst at the Heritage Foundation, said it would be a mistake to put peacekeepers in Israel, given the “poor record of previous monitors.” “In general, the Bush administration policy is to discourage a large American presence,” he said. “But it has been rumored that one of the possibilities might be an expanded CIA role.” “It would be a very different environment than Bosnia,” said Mr. Phillips, referring to America’s six-year peacekeeping role in Bosnia-Herzegovina. “The Palestinian Authority is pushing for this as part of its strategy to internationalize the conflict. Bring in the Europeans and Russia and China. But such monitors or peacekeeping forces are not going to be able to bring peace. Only a decision by the Palestinians to stop the violence and restart talks could possibly do that.”
<<https://www.ord.io/70787305>>
<<<https://www.ord.io/74522515>>>
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 87e98bb6:8d6616f4
2025-05-23 15:36:32
@ 87e98bb6:8d6616f4
2025-05-23 15:36:32Use this guide if you want to keep your NixOS on the stable branch, but enable unstable application packages. It took me a while to figure out how to do this, so I wanted to share because it ended up being far easier than most of the vague explanations online made it seem.
I put a sample configuration.nix file at the very bottom to help it make more sense for new users. Remember to keep a backup of your config file, just in case!
If there are any errors please let me know. I am currently running NixOS 24.11.
Steps listed in this guide: 1. Add the unstable channel to NixOS as a secondary channel. 2. Edit the configuration.nix to enable unstable applications. 3. Add "unstable." in front of the application names in the config file (example: unstable.program). This enables the install of unstable versions during the build. 4. Rebuild.
Step 1:
- Open the console. (If you want to see which channels you currently have, type: sudo nix-channel --list)
- Add the unstable channel, type: sudo nix-channel --add https://channels.nixos.org/nixpkgs-unstable unstable
- To update the channels (bring in the possible apps), type: sudo nix-channel --update
More info here: https://nixos.wiki/wiki/Nix_channels
Step 2:
Edit your configuration.nix and add the following around your current config:
``` { config, pkgs, lib, ... }:
let unstable = import
{ config = { allowUnfree = true; }; }; in { #insert normal configuration text here } #remember to close the bracket!```
At this point it would be good to save your config and try a rebuild to make sure there are no errors. If you have errors, make sure your brackets are in the right places and/or not missing. This step will make for less troubleshooting later on if something happens to be in the wrong spot!
Step 3:
Add "unstable." to the start of each application you want to use the unstable version. (Example: unstable.brave)
Step 4:
Rebuild your config, type: sudo nixos-rebuild switch
Example configuration.nix file:
```
Config file for NixOS
{ config, pkgs, lib, ... }:
Enable unstable apps from Nix repository.
let unstable = import
{ config = { allowUnfree = true; }; }; in { #Put your normal config entries here in between the tags. Below is what your applications list needs to look like.
environment.systemPackages = with pkgs; [ appimage-run blender unstable.brave #Just add unstable. before the application name to enable the unstable version. chirp discord ];
} # Don't forget to close bracket at the end of the config file!
``` That should be all. Hope it helps.
-
 @ 3bf0c63f:aefa459d
2025-04-25 18:55:52
@ 3bf0c63f:aefa459d
2025-04-25 18:55:52Report of how the money Jack donated to the cause in December 2022 has been misused so far.
Bounties given
March 2025
- Dhalsim: 1,110,540 - Work on Nostr wiki data processing
February 2025
- BOUNTY* NullKotlinDev: 950,480 - Twine RSS reader Nostr integration
- Dhalsim: 2,094,584 - Work on Hypothes.is Nostr fork
- Constant, Biz and J: 11,700,588 - Nostr Special Forces
January 2025
- Constant, Biz and J: 11,610,987 - Nostr Special Forces
- BOUNTY* NullKotlinDev: 843,840 - Feeder RSS reader Nostr integration
- BOUNTY* NullKotlinDev: 797,500 - ReadYou RSS reader Nostr integration
December 2024
- BOUNTY* tijl: 1,679,500 - Nostr integration into RSS readers yarr and miniflux
- Constant, Biz and J: 10,736,166 - Nostr Special Forces
- Thereza: 1,020,000 - Podcast outreach initiative
November 2024
- Constant, Biz and J: 5,422,464 - Nostr Special Forces
October 2024
- Nostrdam: 300,000 - hackathon prize
- Svetski: 5,000,000 - Latin America Nostr events contribution
- Quentin: 5,000,000 - nostrcheck.me
June 2024
- Darashi: 5,000,000 - maintaining nos.today, searchnos, search.nos.today and other experiments
- Toshiya: 5,000,000 - keeping the NIPs repo clean and other stuff
May 2024
- James: 3,500,000 - https://github.com/jamesmagoo/nostr-writer
- Yakihonne: 5,000,000 - spreading the word in Asia
- Dashu: 9,000,000 - https://github.com/haorendashu/nostrmo
February 2024
- Viktor: 5,000,000 - https://github.com/viktorvsk/saltivka and https://github.com/viktorvsk/knowstr
- Eric T: 5,000,000 - https://github.com/tcheeric/nostr-java
- Semisol: 5,000,000 - https://relay.noswhere.com/ and https://hist.nostr.land relays
- Sebastian: 5,000,000 - Drupal stuff and nostr-php work
- tijl: 5,000,000 - Cloudron, Yunohost and Fraidycat attempts
- Null Kotlin Dev: 5,000,000 - AntennaPod attempt
December 2023
- hzrd: 5,000,000 - Nostrudel
- awayuki: 5,000,000 - NOSTOPUS illustrations
- bera: 5,000,000 - getwired.app
- Chris: 5,000,000 - resolvr.io
- NoGood: 10,000,000 - nostrexplained.com stories
October 2023
- SnowCait: 5,000,000 - https://nostter.vercel.app/ and other tools
- Shaun: 10,000,000 - https://yakihonne.com/, events and work on Nostr awareness
- Derek Ross: 10,000,000 - spreading the word around the world
- fmar: 5,000,000 - https://github.com/frnandu/yana
- The Nostr Report: 2,500,000 - curating stuff
- james magoo: 2,500,000 - the Obsidian plugin: https://github.com/jamesmagoo/nostr-writer
August 2023
- Paul Miller: 5,000,000 - JS libraries and cryptography-related work
- BOUNTY tijl: 5,000,000 - https://github.com/github-tijlxyz/wikinostr
- gzuus: 5,000,000 - https://nostree.me/
July 2023
- syusui-s: 5,000,000 - rabbit, a tweetdeck-like Nostr client: https://syusui-s.github.io/rabbit/
- kojira: 5,000,000 - Nostr fanzine, Nostr discussion groups in Japan, hardware experiments
- darashi: 5,000,000 - https://github.com/darashi/nos.today, https://github.com/darashi/searchnos, https://github.com/darashi/murasaki
- jeff g: 5,000,000 - https://nostr.how and https://listr.lol, plus other contributions
- cloud fodder: 5,000,000 - https://nostr1.com (open-source)
- utxo.one: 5,000,000 - https://relaying.io (open-source)
- Max DeMarco: 10,269,507 - https://www.youtube.com/watch?v=aA-jiiepOrE
- BOUNTY optout21: 1,000,000 - https://github.com/optout21/nip41-proto0 (proposed nip41 CLI)
- BOUNTY Leo: 1,000,000 - https://github.com/leo-lox/camelus (an old relay thing I forgot exactly)
June 2023
- BOUNTY: Sepher: 2,000,000 - a webapp for making lists of anything: https://pinstr.app/
- BOUNTY: Kieran: 10,000,000 - implement gossip algorithm on Snort, implement all the other nice things: manual relay selection, following hints etc.
- Mattn: 5,000,000 - a myriad of projects and contributions to Nostr projects: https://github.com/search?q=owner%3Amattn+nostr&type=code
- BOUNTY: lynn: 2,000,000 - a simple and clean git nostr CLI written in Go, compatible with William's original git-nostr-tools; and implement threaded comments on https://github.com/fiatjaf/nocomment.
- Jack Chakany: 5,000,000 - https://github.com/jacany/nblog
- BOUNTY: Dan: 2,000,000 - https://metadata.nostr.com/
April 2023
- BOUNTY: Blake Jakopovic: 590,000 - event deleter tool, NIP dependency organization
- BOUNTY: koalasat: 1,000,000 - display relays
- BOUNTY: Mike Dilger: 4,000,000 - display relays, follow event hints (Gossip)
- BOUNTY: kaiwolfram: 5,000,000 - display relays, follow event hints, choose relays to publish (Nozzle)
- Daniele Tonon: 3,000,000 - Gossip
- bu5hm4nn: 3,000,000 - Gossip
- BOUNTY: hodlbod: 4,000,000 - display relays, follow event hints
March 2023
- Doug Hoyte: 5,000,000 sats - https://github.com/hoytech/strfry
- Alex Gleason: 5,000,000 sats - https://gitlab.com/soapbox-pub/mostr
- verbiricha: 5,000,000 sats - https://badges.page/, https://habla.news/
- talvasconcelos: 5,000,000 sats - https://migrate.nostr.com, https://read.nostr.com, https://write.nostr.com/
- BOUNTY: Gossip model: 5,000,000 - https://camelus.app/
- BOUNTY: Gossip model: 5,000,000 - https://github.com/kaiwolfram/Nozzle
- BOUNTY: Bounty Manager: 5,000,000 - https://nostrbounties.com/
February 2023
- styppo: 5,000,000 sats - https://hamstr.to/
- sandwich: 5,000,000 sats - https://nostr.watch/
- BOUNTY: Relay-centric client designs: 5,000,000 sats https://bountsr.org/design/2023/01/26/relay-based-design.html
- BOUNTY: Gossip model on https://coracle.social/: 5,000,000 sats
- Nostrovia Podcast: 3,000,000 sats - https://nostrovia.org/
- BOUNTY: Nostr-Desk / Monstr: 5,000,000 sats - https://github.com/alemmens/monstr
- Mike Dilger: 5,000,000 sats - https://github.com/mikedilger/gossip
January 2023
- ismyhc: 5,000,000 sats - https://github.com/Galaxoid-Labs/Seer
- Martti Malmi: 5,000,000 sats - https://iris.to/
- Carlos Autonomous: 5,000,000 sats - https://github.com/BrightonBTC/bija
- Koala Sat: 5,000,000 - https://github.com/KoalaSat/nostros
- Vitor Pamplona: 5,000,000 - https://github.com/vitorpamplona/amethyst
- Cameri: 5,000,000 - https://github.com/Cameri/nostream
December 2022
- William Casarin: 7 BTC - splitting the fund
- pseudozach: 5,000,000 sats - https://nostr.directory/
- Sondre Bjellas: 5,000,000 sats - https://notes.blockcore.net/
- Null Dev: 5,000,000 sats - https://github.com/KotlinGeekDev/Nosky
- Blake Jakopovic: 5,000,000 sats - https://github.com/blakejakopovic/nostcat, https://github.com/blakejakopovic/nostreq and https://github.com/blakejakopovic/NostrEventPlayground
-
 @ 6d5c826a:4b27b659
2025-05-23 21:46:11
@ 6d5c826a:4b27b659
2025-05-23 21:46:11- GLPI - Information Resource-Manager with an additional Administration Interface. (Source Code)
GPL-3.0PHP - OCS Inventory NG - Asset management and deployment solution for all devices in your IT Department. (Source Code)
GPL-2.0PHP/Perl - OPSI - Hardware and software inventory, client management, deployment, and patching for Linux and Windows. (Source Code)
GPL-3.0/AGPL-3.0OVF/Python - RackTables - Datacenter and server room asset management like document hardware assets, network addresses, space in racks, networks configuration. (Demo, Source Code)
GPL-2.0PHP - Ralph - Asset management, DCIM and CMDB system for large Data Centers as well as smaller LAN networks. (Demo, Source Code)
Apache-2.0Python/Docker - Snipe IT - Asset & license management software. (Source Code)
AGPL-3.0PHP
- GLPI - Information Resource-Manager with an additional Administration Interface. (Source Code)
-
 @ b2caa9b3:9eab0fb5
2025-04-24 06:25:35
@ b2caa9b3:9eab0fb5
2025-04-24 06:25:35Yesterday, I faced one of the most heartbreaking and frustrating experiences of my life. Between 10:00 AM and 2:00 PM, I was held at the Taveta border, denied entry into Kenya—despite having all the necessary documents, including a valid visitor’s permit and an official invitation letter.
The Kenyan Immigration officers refused to speak with me. When I asked for clarification, I was told flatly that I would never be allowed to enter Kenya unless I obtain a work permit. No other reason was given. My attempts to explain that I simply wanted to see my child were ignored. No empathy. No flexibility. No conversation. Just rejection.
While I stood there for hours, held by officials with no explanation beyond a bureaucratic wall, I recorded the experience. I now have several hours of footage documenting what happened—a silent testimony to how a system can dehumanize and block basic rights.
And the situation doesn’t end at the border.
My child, born in Kenya, is also being denied the right to see me. Germany refuses to grant her citizenship, which means she cannot visit me either. The German embassy in Nairobi refuses to assist, stating they won’t get involved. Their silence is loud.
This is not just about paperwork. This is about a child growing up without her father. It’s about a system that chooses walls over bridges, and bureaucracy over humanity. Kenya, by refusing me entry, is keeping a father away from his child. Germany, by refusing to act under §13 StGB, is complicit in that injustice.
In the coming days, I’ll share more about my past travels and how this situation unfolded. I’ll also be releasing videos and updates on TikTok—because this story needs to be heard. Not just for me, but for every parent and child caught between borders and bureaucracies.
Stay tuned—and thank you for standing with me.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:45:53
@ 6d5c826a:4b27b659
2025-05-23 21:45:53- BounCA - A personal SSL Key / Certificate Authority web-based tool for creating self-signed certificates. (Source Code)
Apache-2.0Python - easy-rsa - Bash script to build and manage a PKI CA.
GPL-2.0Shell - Fusion Directory - Improve the Management of the services and the company directory based on OpenLDAP. (Source Code)
GPL-2.0PHP - LDAP Account Manager (LAM) - Web frontend for managing entries (e.g. users, groups, DHCP settings) stored in an LDAP directory. (Source Code)
GPL-3.0PHP - Libravatar - Libravatar is a service which delivers your avatar (profile picture) to other websites. (Source Code)
AGPL-3.0Python - Pomerium - An identity and context aware access-proxy inspired by BeyondCorp. (Source Code)
Apache-2.0Docker/Go - Samba - Active Directory and CIFS protocol implementation. (Source Code)
GPL-3.0C - Smallstep Certificates - A private certificate authority (X.509 & SSH) and related tools for secure automated certificate management. (Source Code)
Apache-2.0Go - ZITADEL - Cloud-native Identity & Access Management solution providing a platform for secure authentication, authorization and identity management. (Source Code)
Apache-2.0Go/Docker/K8S
- BounCA - A personal SSL Key / Certificate Authority web-based tool for creating self-signed certificates. (Source Code)
-
 @ 10f7c7f7:f5683da9
2025-05-23 15:26:17
@ 10f7c7f7:f5683da9
2025-05-23 15:26:17While I’m going to stand by what I said in my previous piece, minimise capital gains payments, don’t fund the government, get a loan against your bitcoin, but the wheels in my left curve brain have continued to turn, well that, and a few more of my 40PW insights. I mentioned about paying attention to the risks involved in terms of borrowing against your bitcoin, and hopefully ending up paying less in bitcoin at the end of the loan, even if you ultimately sold bitcoin to pay off the loan. However, the idea of losing control of the bitcoin I have spent a good deal of time and effort accumulating being out of my control has led me to reconsider. I also realised I didn’t fully flesh out some other topics that I think are relevant, not least time preference, specifically in relation to what you’re buying. The idea of realising a lump some of capital to live your dreams, buy a house or a cool car may be important, but it may be worth taking a step back and looking at what you’re purchasing. Are you only purchasing those things because you had been able to get this new money “tax free”? If that is the case, and the fiat is burning a hold in your pocket, maybe you’ve just found yourself with the same fiat brained mentality you have been working so hard to escape from while you have sacrificed and saved to stack sats.
While it may no longer be necessary to ask yourself whether a particular product or service is worth selling your bitcoin for because you’ve taken out a loan, it may still be worth asking yourself whether a particular loan fuelled purchase is worth forfeiting control of your keys for? Unlike the foolish 18 year-old, released into a world with their newly preapproved credit card, you need to take a moment and ask yourself:
Is the risk worth it?
Is the purchase worth it?
But also take a moment to consider a number of other things, are there fiat options?
Where in the cycle might you be?
Or if I’m thinking carefully about this, will whatever I’m buying hold its value (experiences may be more difficult to run the numbers on)?
The reason for asking these things, is that if you still have a foot in the fiat world, dealing with a fiat bank account, fiat institutions may still be very willing to provide you with a loan at a lower rate than a bitcoin backed loan. Particularly if you’re planning on using that money to buy a house; if you can qualify for a mortgage, get a mortgage, but if you need cash for a deposit, maybe that is where the bitcoin backed loan may come in. Then, it may be worth thinking about where are you in the bitcoin cycle? No one can answer this, but with the historic data we have, it appears logical that after some type of run up, prices may retrace (Dan Held’s supercycle withstanding).
Matteo Pellegrini with Daniel Prince provided a new perspective on this for me. Rather the riding the bull market gains all the way through to the bear market bottom, what happens if I chose to buy an asset that didn’t lose quite as much fiat value as bitcoin, for example, a Swiss Watch, or a tasteful, more mature sports car? If that was the purchase of choice, they suggested that you could enjoy the car, “the experience” for a year or two, then realise the four door estate was likely always the better option, sell it and be able to buy back as many, if not slightly more bitcoin that you originally sold (not financial, classic car or price prediction advice, I’m not accredited to advise pretty much anything). Having said that, it is a scenario I think worth thinking about when the bitcoin denominated dream car begins to make financial sense.
Then, as we begin to look forward to the near inevitable bear market (they are good for both stacking and grinding), if we’ve decided to take out a loan rather than sell, we then may ultimately need to increase our collateral to maintain loan to value requirements, as well as sell more bitcoin to cover repayments (if that’s the route we’re taking). This then moves us back into the domain of saying, well in actual fact we should just sell our bitcoin when we can get most dollar for it (or the coolest car), with a little extra to cover future taxes, it is probably better to sell near a top than a bottom. The balance between these two rather extreme positions could be to take out a fiat loan to buy the item and maybe sell sufficient bitcoin so you’re able to cover the loan for a period of time (less taxable events to keep track of and also deals with future uncertainty of bitcoin price). In this case, if the loan timeframe is longer than the amount of loan your sale can cover, by the time you need to sell anymore, the price should have recovered from a cycle bottom.
In this scenario, apart from the smaller portion of bitcoin you have had to sell, the majority of your stack can remain in cold storage, the loan you took out will be unsecured (particularly against your bitcoin), but even if it isn’t, the value of what you purchase maintains its value, you can in theory exit the loan at any point by selling the luxury item. Then within this scenario, if you had sold near a top, realised the car gave you a bad back or made you realise you staying humble is more important, sold it, paid off the loan, there may even be a chance you could buy back more bitcoin with the money you had left over from selling your bitcoin to fund the loan.
I have no idea of this could actually work, but to be honest, I’m looking forward to trying it out in the next 6-12 months, although I may keep my daily driver outside of my bitcoin strategy (kids still need a taxi service). Having said that, I think there are some important points to consider in addition to not paying capital gains tax (legally), as well as the opportunities of bitcoin loans. They are still very young products and to quote every trad-fi news outlet, “bitcoin is still a volatile asset”, these thought experiments are still worth working through. To push back on the Uber fiat journalist, Katie Martin, “Bitcoin has no obvious use case”, it does, it can be a store of value to hold or sell, it can be liquid and flexible collateral, but also an asset that moves independently of other assets to balance against fiat liabilities. The idea of being able to release some capital, enjoy the benefits of the capital for a period, before returning that capital to store value feels like a compelling one.
The important thing to remember is that there are a variety of options, whether selling for cash, taking out a bitcoin backed loan, taking out a fiat loan or some combination of each. Saying that, what I would think remains an important question to ask irrespective of the option you go for:
Is what I’m planning on buying, worth selling bitcoin for?
If it cannot pass this first question, maybe it isn’t worth purchasing to start with.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:45:34
@ 6d5c826a:4b27b659
2025-05-23 21:45:34- Authelia - The Single Sign-On Multi-Factor portal for web apps. (Source Code)
Apache-2.0Go - Authentik - Flexible identity provider with support for different protocols. (OAuth 2.0, SAML, LDAP and Radius). (Source Code)
MITPython - KeyCloak - Open Source Identity and Access Management. (Source Code)
Apache-2.0Java
- Authelia - The Single Sign-On Multi-Factor portal for web apps. (Source Code)
-
 @ a39d19ec:3d88f61e
2025-04-22 12:44:42
@ a39d19ec:3d88f61e
2025-04-22 12:44:42Die Debatte um Migration, Grenzsicherung und Abschiebungen wird in Deutschland meist emotional geführt. Wer fordert, dass illegale Einwanderer abgeschoben werden, sieht sich nicht selten dem Vorwurf des Rassismus ausgesetzt. Doch dieser Vorwurf ist nicht nur sachlich unbegründet, sondern verkehrt die Realität ins Gegenteil: Tatsächlich sind es gerade diejenigen, die hinter jeder Forderung nach Rechtssicherheit eine rassistische Motivation vermuten, die selbst in erster Linie nach Hautfarbe, Herkunft oder Nationalität urteilen.
Das Recht steht über Emotionen
Deutschland ist ein Rechtsstaat. Das bedeutet, dass Regeln nicht nach Bauchgefühl oder politischer Stimmungslage ausgelegt werden können, sondern auf klaren gesetzlichen Grundlagen beruhen müssen. Einer dieser Grundsätze ist in Artikel 16a des Grundgesetzes verankert. Dort heißt es:
„Auf Absatz 1 [Asylrecht] kann sich nicht berufen, wer aus einem Mitgliedstaat der Europäischen Gemeinschaften oder aus einem anderen Drittstaat einreist, in dem die Anwendung des Abkommens über die Rechtsstellung der Flüchtlinge und der Europäischen Menschenrechtskonvention sichergestellt ist.“
Das bedeutet, dass jeder, der über sichere Drittstaaten nach Deutschland einreist, keinen Anspruch auf Asyl hat. Wer dennoch bleibt, hält sich illegal im Land auf und unterliegt den geltenden Regelungen zur Rückführung. Die Forderung nach Abschiebungen ist daher nichts anderes als die Forderung nach der Einhaltung von Recht und Gesetz.
Die Umkehrung des Rassismusbegriffs
Wer einerseits behauptet, dass das deutsche Asyl- und Aufenthaltsrecht strikt durchgesetzt werden soll, und andererseits nicht nach Herkunft oder Hautfarbe unterscheidet, handelt wertneutral. Diejenigen jedoch, die in einer solchen Forderung nach Rechtsstaatlichkeit einen rassistischen Unterton sehen, projizieren ihre eigenen Denkmuster auf andere: Sie unterstellen, dass die Debatte ausschließlich entlang ethnischer, rassistischer oder nationaler Kriterien geführt wird – und genau das ist eine rassistische Denkweise.
Jemand, der illegale Einwanderung kritisiert, tut dies nicht, weil ihn die Herkunft der Menschen interessiert, sondern weil er den Rechtsstaat respektiert. Hingegen erkennt jemand, der hinter dieser Kritik Rassismus wittert, offenbar in erster Linie die „Rasse“ oder Herkunft der betreffenden Personen und reduziert sie darauf.
Finanzielle Belastung statt ideologischer Debatte
Neben der rechtlichen gibt es auch eine ökonomische Komponente. Der deutsche Wohlfahrtsstaat basiert auf einem Solidarprinzip: Die Bürger zahlen in das System ein, um sich gegenseitig in schwierigen Zeiten zu unterstützen. Dieser Wohlstand wurde über Generationen hinweg von denjenigen erarbeitet, die hier seit langem leben. Die Priorität liegt daher darauf, die vorhandenen Mittel zuerst unter denjenigen zu verteilen, die durch Steuern, Sozialabgaben und Arbeit zum Erhalt dieses Systems beitragen – nicht unter denen, die sich durch illegale Einreise und fehlende wirtschaftliche Eigenleistung in das System begeben.
Das ist keine ideologische Frage, sondern eine rein wirtschaftliche Abwägung. Ein Sozialsystem kann nur dann nachhaltig funktionieren, wenn es nicht unbegrenzt belastet wird. Würde Deutschland keine klaren Regeln zur Einwanderung und Abschiebung haben, würde dies unweigerlich zur Überlastung des Sozialstaates führen – mit negativen Konsequenzen für alle.
Sozialpatriotismus
Ein weiterer wichtiger Aspekt ist der Schutz der Arbeitsleistung jener Generationen, die Deutschland nach dem Zweiten Weltkrieg mühsam wieder aufgebaut haben. Während oft betont wird, dass die Deutschen moralisch kein Erbe aus der Zeit vor 1945 beanspruchen dürfen – außer der Verantwortung für den Holocaust –, ist es umso bedeutsamer, das neue Erbe nach 1945 zu respektieren, das auf Fleiß, Disziplin und harter Arbeit beruht. Der Wiederaufbau war eine kollektive Leistung deutscher Menschen, deren Früchte nicht bedenkenlos verteilt werden dürfen, sondern vorrangig denjenigen zugutekommen sollten, die dieses Fundament mitgeschaffen oder es über Generationen mitgetragen haben.
Rechtstaatlichkeit ist nicht verhandelbar
Wer sich für eine konsequente Abschiebepraxis ausspricht, tut dies nicht aus rassistischen Motiven, sondern aus Respekt vor der Rechtsstaatlichkeit und den wirtschaftlichen Grundlagen des Landes. Der Vorwurf des Rassismus in diesem Kontext ist daher nicht nur falsch, sondern entlarvt eine selektive Wahrnehmung nach rassistischen Merkmalen bei denjenigen, die ihn erheben.
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:45:15
@ 6d5c826a:4b27b659
2025-05-23 21:45:15- 389 Directory Server - Enterprise-class Open Source LDAP server for Linux. (Source Code)
GPL-3.0C - Apache Directory Server - Extensible and embeddable directory server, certified LDAPv3 compatible, with Kerberos 5 and Change Password Protocol support, triggers, stored procedures, queues and views. (Source Code)
Apache-2.0Java - FreeIPA - Integrated security information management solution combining Linux (Fedora), 389 Directory Server, Kerberos, NTP, DNS, and Dogtag Certificate System (web interface and command-line administration tools). (Source Code)
GPL-3.0Python/C/JavaScript - FreeRADIUS - Multi-protocol policy server (radiusd) that implements RADIUS, DHCP, BFD, and ARP and associated client/PAM library/Apache module. (Source Code)
GPL-2.0C - lldap - Light (simplified) LDAP implementation with a simple, intuitive web interface and GraphQL support.
GPL-3.0Rust - OpenLDAP - Open-source implementation of the Lightweight Directory Access Protocol (server, libraries and clients). (Source Code)
OLDAP-2.8C
- 389 Directory Server - Enterprise-class Open Source LDAP server for Linux. (Source Code)
-
 @ cae03c48:2a7d6671
2025-05-23 14:01:07
@ cae03c48:2a7d6671
2025-05-23 14:01:07Bitcoin Magazine

KindlyMD, Nakamoto, and Anchorage Digital Form Strategic Bitcoin Treasury AllianceNakamoto Holdings Inc., KindlyMD, Inc., and Anchorage Digital today announced a strategic partnership that will see Anchorage become a trading partner for KindlyMD’s Bitcoin treasury. The partnership will officially take effect upon the close of KindlyMD’s merger with Nakamoto, expected in Q3 2025.
NEW! Anchorage Digital
 @Nakamoto @KindlyMD
@Nakamoto @KindlyMD Today we’re thrilled to announce a strategic partnership with Nakamoto Holdings and $KDLY to accelerate the future of corporate Bitcoin adoption. pic.twitter.com/nQueTyutQH
— Anchorage Digital
 (@Anchorage) May 21, 2025
(@Anchorage) May 21, 2025Anchorage Digital, a U.S. federally chartered digital asset bank, will provide institutional-grade custody, 24/7 trading, and deep liquidity to support the Bitcoin strategy of the combined entity.
“In the not-so-distant-future, the omission of Bitcoin on a balance sheet will be more glaring than its inclusion,” said Nathan McCauley, CEO and Co-Founder of Anchorage Digital. “Until then, companies like Nakamoto-KindlyMD are pioneering a new path forward—one in which Bitcoin is at the heart of corporate strategy.”
The future of corporate treasury strategy is Bitcoin-native. We're here to make it happen. Pumped to be partnering with @Nakamoto and @KindlyMD.@DavidFBailey’s vision continues to open new doors.
— Nathan McCauley
 (@nathanmccauley) May 21, 2025
(@nathanmccauley) May 21, 2025The merger between KindlyMD and Nakamoto is backed by approximately $710 million in financing, including $510 million in PIPE funding—the largest ever PIPE for a public crypto-related deal. The goal is to establish a Bitcoin-native corporate treasury strategy that redefines how capital markets engage with digital assets.
“Our goal is to bring Bitcoin to the center of global capital markets within a compliant, transparent structure,” said David Bailey, Founder and CEO of Nakamoto Holdings Inc. “We are excited to partner with Anchorage Digital to implement our vision with the highest levels of security and battle-tested infrastructure and enable us to deliver sustained value to shareholders.”
This announcement follows a key milestone on May 18, when KindlyMD shareholders approved the proposed merger with Nakamoto. The transaction is now expected to close in Q3 2025, pending SEC review and information statement distribution.
“This milestone brings us one step closer to unlocking Bitcoin’s potential for KindlyMD shareholders,” Bailey said yesterday. “We are grateful that KindlyMD shares our vision for a future in which Bitcoin is a core part of the corporate balance sheet.”
With its Bitcoin-first strategy and strategic alliances, the Nakamoto-KindlyMD partnership is set to accelerate institutional Bitcoin adoption—and with Anchorage Digital’s infrastructure behind it, the foundation is now firmly in place.
“By collaborating with Anchorage Digital, we are implementing our Bitcoin treasury strategy with the utmost standards in safety and security for our shareholders,” stated Tim Pickett, CEO of KindlyMD. “Their institutional-grade platform allows us to confidently hold Bitcoin as a treasury asset as we look to unlock access to Bitcoin and drive value for the long term.”
Disclosure: Nakamoto is in partnership with Bitcoin Magazine’s parent company BTC Inc to build the first global network of Bitcoin treasury companies, where BTC Inc provides certain marketing services to Nakamoto. More information on this can be found here.
This post KindlyMD, Nakamoto, and Anchorage Digital Form Strategic Bitcoin Treasury Alliance first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 6d5c826a:4b27b659
2025-05-23 21:44:57
@ 6d5c826a:4b27b659
2025-05-23 21:44:57- Atom Community - A fork of atom A hackable text editor from Github.
MITJavaScript - Brackets - Code editor for web designers and front-end developers. (Source Code)
MITJavaScript - Eclipse - IDE written in Java with an extensible plug-in system. (Source Code)
EPL-1.0Java - Geany - GTK2 text editor. (Source Code)
GPL-2.0C/C++ - GNU Emacs - An extensible, customizable text editor-and more. (Source Code)
GPL-3.0C - Haroopad - Markdown editor with live preview. (Source Code)
GPL-3.0JavaScript - jotgit - Git-backed real-time collaborative code editing.
MITNodejs - KDevelop - IDE by the people behind KDE. (Source Code)
GFDL-1.2C++ - Micro - A modern and intuitive terminal-based text editor. (Source Code)
MITGo - Nano - Easy to use, customizable text editor. (Source Code)
GPL-3.0C - Notepad++ - GPLv2 multi-language editor with syntax highlighting for Windows. (Source Code)
GPL-2.0C++ - TextMate - A graphical text editor for OS X. (Source Code)
GPL-3.0C++ - Vim - A highly configurable text editor built to enable efficient editing. (Source Code)
VimC - VSCodium - An open source cross-platform extensible code editor based on VS Code by Microsoft removing their non-free additions. (Source Code)
MITTypeScript
- Atom Community - A fork of atom A hackable text editor from Github.
-
 @ cae03c48:2a7d6671
2025-05-23 14:01:05
@ cae03c48:2a7d6671
2025-05-23 14:01:05Bitcoin Magazine

How Zeus is Redefining Bitcoin with Cashu Ecash IntegrationThe U.S.-based Bitcoin and Lightning mobile wallet Zeus recently announced an alpha-release integration of Cashu. The move marks the first integration of ecash into a popular Bitcoin wallet, breaking new ground for potential user adoption to Bitcoin.
Cashu is a hot new implementation of Chaumian ecash, a form of digital cash invented by David Chaum in the ’90s that has incredible privacy and scalability properties, with the trade-off of being fundamentally centralized, requiring a significant amount of trust in the issuer.

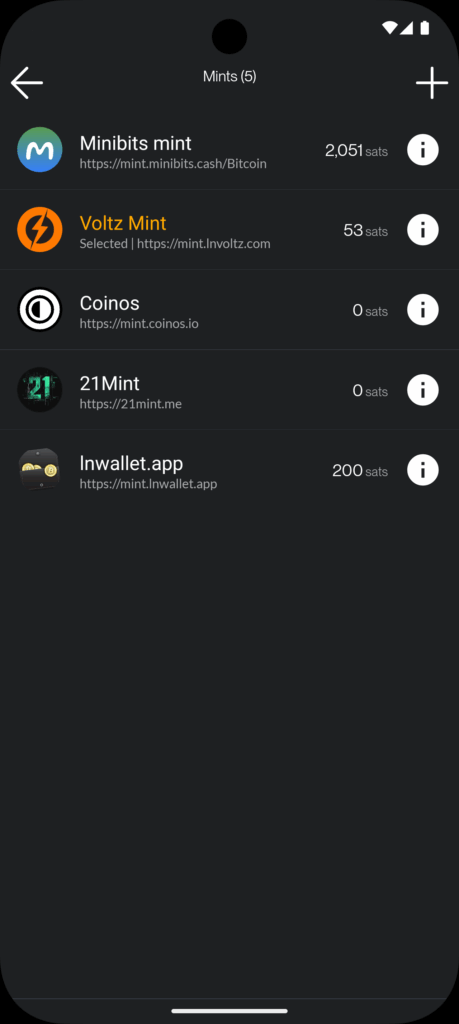
In a counterintuitive move for Zeus, known as the go-to tool for advanced Lightning users seeking to connect to their home nodes, the integration of Cashu acknowledges a “last mile” challenge Lightning wallets face when delivering Bitcoin to the masses.
“We basically started off as the cypherpunk wallet, right? You got to set up your own Lightning node and connect to it with Zeus. The last two years, we put the node in the phone with one click, you can run it all in a standalone app without a remote node,” Evan Kaloudis, founder and CEO of Zeus, told Bitcoin Magazine.
“Cashu addresses uneconomical self-custody for small bitcoin amounts. On-chain, the dust limit is 546 satoshis, and Layer Two systems like Lightning have costs for channel setup or unilateral exits that aren’t widely discussed,” Evan explained, highlighting a major point of friction in noncustodial Lightning wallets: the need for liquidity and channel management. While these esoteric aspects of the Lightning Network have been mostly abstracted away since its invention in 2016, these fundamental trade-offs continue to manifest even in the most sophisticated and user-friendly wallets.
In the case of both Phoenix and Zeus, two of the most popular noncustodial options in the market, users must pay up to 10,000 sats upfront to gain spending capacity. These fees are necessary to cover the on-chain fees spent to open a channel for the user against the wallet’s liquidity service provider, unlocking a noncustodial experience.
The required up-front fee is difficult to explain and represents a painful onboarding experience for new users who are used to fiat apps giving them money to join instead. The result is the proliferation of custodial Lightning wallets like Wallet of Satoshi (WOS), which gained massive adoption early on by leveraging the global, near-instant settlement power of Bitcoin combined with the excellent user experience centralized wallets can create.
Major developments have been made over seven years after the Lightning Network’s inception, however, and Zeus is pushing the boundaries.
“With Ecash, we make it so easy that anyone can set up a wallet and start participating in our ecosystem, which I really think is going to become more and more prevalent,” Evan explained.
Today, at roughly $100,000 per bitcoin, 1,000 satoshis are equivalent to $1. Transactions of these sizes are known as microtransactions — a popular example are Nostr social media tips known as Zaps. But finding the right tool for this use case is not simple. Self custodied wallets like Phoenix charge transaction fees in the hundreds of satoshis, even with open channels, and on-chain fees often cost the same and are slower to settle. As a result, there’s an entire category of spending that is only served by cheaper alternatives such as custodial lightning wallets like WOS or Blink, but result in significant privacy tradeoffs, often requiring phone numbers from users and in some cases more advanced KYC and IP tracking. Cashu hopes to serve this market with lower privacy costs, the same ease of use, speed and competitive fees.
Digging deeper into the Cashu integration, Evan explained that “for users this means being able to pick and switch between custodians in a single app. For developers this means being able to defer custodial responsibilities to third parties and not have to wire up a new integration when your current custodian halts operations.”
Zaps are satoshi-denominated rewards delivered as “likes” or micro-tips for content in the Nostr social media ecosystem. A Zap can be as small as one satoshi, the smallest amount of bitcoin that can be technically transferred, equivalent today to about a tenth of a penny. “But I think if we look at Nostr and you’re seeing how many people are Zapping and how big a part of that ecosystem it is. It’s like, people are willing to do it,” Evan explained.
“Cashu, while custodial, lets users accumulate small amounts — say, via Nostr Zaps — without needing 6,000 satoshis to open a Lightning channel. Zeus prompts users to upgrade to self-custody as their balance grows,” he concluded, explaining that the wallet will effectively annoy users into self custody, one of several design choices made to mitigate the risks introduced by Cashu.
Ecash
The trade-offs introduced by Cashu challenge the common understanding of custody as an either-or in Bitcoin. Historically you were either a centralized — custodial — exchange, or you were a noncustodial Bitcoin wallet. In the former, you entrust the coins to a third party; in the latter you take personal responsibility for those coins and their corresponding private keys. Cashu changes this paradigm by introducing bitcoin-denominated ecash notes or “nuts,” which are bearer instruments that should be backed by a full bitcoin reserve and Lightning interoperability for instant withdraw.
Similar to fiat cash, you must take control and responsibility over these notes, but there’s also counterparty risk. In the case of Cashu, there are certain things the issuing mint can theoretically do to exploit their users — akin to how a bank can run on a fractional reserve.
The big difference between Cashu or custodial Bitcoin exchanges and fiat currency is that Cashu is open source, is designed around user privacy, and scales very well. It makes the cost of running a mint lower than either alternative, a feature that makes mint competition easier, in theory countering the centralizing network effects of specific mints.
Finally, the user experience of storing Cashu tokens has been attached to known forms of Bitcoin self custody such as the download of 12-words seeds via various mechanisms, though implementations still vary from wallet to wallet and the whole ecosystem is in its early stages.
To further mitigate the custodial risk of Chaumian-style ecash in Bitcoin, the Cashu community has developed various methods for automatically managing custody risk.



“Users can split risk by using multiple mints, switching between them in the user interface. Soon, ZEUS will guide users to select five or six reputable mints, automatically balancing funds to minimize exposure,” Evan explained, referring to a particular approach called automated bank runs. The idea is that as some Cashu mints may hold more of your funds, Zeus de-ranks them and rotates value out to minimize risk.
“I think the idea is going to be that we guide users to pick five or six reputable mints… And from there, users will be able to have the wallet automatically switch between those mints and determine which mint should be receiving the balance depending on the balance of all the mints presently. So you’ll be like, OK. MiniBits has way too much money. Let’s switch the default to one of the mints that doesn’t have a lot. So that way you can sort of mitigate or rather distribute the rug risk there,” Evan explained, adding, “Our Discover Mint feature pulls reviews from bitcoinmints.com, showing vouch counts and user feedback, like mint reliability or longevity,” describing the reputation layer stacked on top of the various other risk management mechanisms.
There is no known way to use Chaumian-style ecash in an entirely noncustodial way. So as long as the custody risk can be minimized, the scaling and privacy upside becomes remarkable.
Microtransactions
One of the opportunities that ecash unlocks is microtransactions, the most popular example of which are Nostr Zaps often in single dollar ranges of value transferred, though it applies to small Lightning transactions as well. This use case triggers an important technical question that predates Bitcoin, do microtransactions actually make economic sense?
There’s a long-standing argu
-
 @ 6d5c826a:4b27b659
2025-05-23 21:44:34
@ 6d5c826a:4b27b659
2025-05-23 21:44:34- Bind - Versatile, classic, complete name server software. (Source Code)
MPL-2.0C - CoreDNS - Flexible DNS server. (Source Code)
Apache-2.0Go - djbdns - A collection of DNS applications, including tinydns. (Source Code)
CC0-1.0C - dnsmasq - Provides network infrastructure for small networks: DNS, DHCP, router advertisement and network boot. (Source Code)
GPL-2.0C - Knot - High performance authoritative-only DNS server. (Source Code)
GPL-3.0C - NSD - Authoritative DNS name server developed speed, reliability, stability and security. (Source Code)
BSD-3-ClauseC - PowerDNS Authoritative Server - Versatile nameserver which supports a large number of backends. (Source Code)
GPL-2.0C++ - Unbound - Validating, recursive, and caching DNS resolver. (Source Code)
BSD-3-ClauseC - Yadifa - Clean, small, light and RFC-compliant name server implementation developed from scratch by .eu. (Source Code)
BSD-3-ClauseC
- Bind - Versatile, classic, complete name server software. (Source Code)
-
 @ 9223d2fa:b57e3de7
2025-04-15 02:54:00
@ 9223d2fa:b57e3de7
2025-04-15 02:54:0012,600 steps
-
 @ 6e0ea5d6:0327f353
2025-04-14 15:11:17
@ 6e0ea5d6:0327f353
2025-04-14 15:11:17Ascolta.
We live in times where the average man is measured by the speeches he gives — not by the commitments he keeps. People talk about dreams, goals, promises… but what truly remains is what’s honored in the silence of small gestures, in actions that don’t seek applause, in attitudes unseen — yet speak volumes.
Punctuality, for example. Showing up on time isn’t about the clock. It’s about respect. Respect for another’s time, yes — but more importantly, respect for one’s own word. A man who is late without reason is already running late in his values. And the one who excuses his own lateness with sweet justifications slowly gets used to mediocrity.
Keeping your word is more than fulfilling promises. It is sealing, with the mouth, what the body must later uphold. Every time a man commits to something, he creates a moral debt with his own dignity. And to break that commitment is to declare bankruptcy — not in the eyes of others, but in front of himself.
And debts? Even the small ones — or especially the small ones — are precise thermometers of character. A forgotten sum, an unpaid favor, a commitment left behind… all of these reveal the structure of the inner building that man resides in. He who neglects the small is merely rehearsing for his future collapse.
Life, contrary to what the reckless say, is not built on grand deeds. It is built with small bricks, laid with almost obsessive precision. The truly great man is the one who respects the details — recognizing in them a code of conduct.
In Sicily, especially in the streets of Palermo, I learned early on that there is more nobility in paying a five-euro debt on time than in flaunting riches gained without word, without honor, without dignity.
As they say in Palermo: L’uomo si conosce dalle piccole cose.
So, amico mio, Don’t talk to me about greatness if you can’t show up on time. Don’t talk to me about respect if your word is fickle. And above all, don’t talk to me about honor if you still owe what you once promised — no matter how small.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ cae03c48:2a7d6671
2025-05-23 14:01:04
@ cae03c48:2a7d6671
2025-05-23 14:01:04Bitcoin Magazine

Bitcoin Liquid Network Surpasses $3.27 Billion in Total Value LockedToday, the Liquid Federation has announced that the Liquid Network has surpassed $3.27 billion in total value locked (TVL), according to a press release shared with Bitcoin Magazine.
“Surpassing the $3 billion threshold marks a pivotal moment for both Liquid and Bitcoin, signaling the evolution of Bitcoinʼs ecosystem into a full-fledged platform for global financial markets,” said the CEO and Co-Founder of Blockstream Dr. Adam Back. “As Bitcoin gains mainstream acceptance, and demand for regulated asset tokenization accelerates, Liquid is better positioned than ever to bridge Bitcoin with traditional finance and drive the next wave of capital markets innovation.”
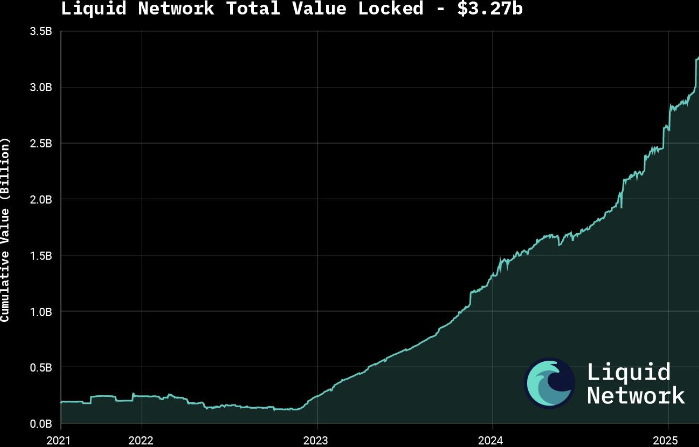
The announcement follows growing interest in tokenizing real-world assets (RWAs), with major moves such as BlackRock’s decision to tokenize a $150 billion Treasury fund. According to a 2025 report by Security Token Market, the tokenized asset market is projected to grow to $30 trillion by 2030.
Liquid supports over $1.8 billion in tokenized private credit and offers products like U.S. Treasury notes and digital currencies through Blockstream’s AMP platform. The network also features fast, low-cost, and confidential transactions, with support for atomic swaps and robust smart contracts.
Governed by over 80 global institutions, Liquid was launched in 2018 as Bitcoin’s first sidechain. It is now preparing for a major upgrade with the mainnet release of Simplicity, aimed at expanding its smart contract capabilities.
To keep up with increasing demand, the Liquid Federation is boosting developer resources and technical onboardings, along with integrations with exchanges, custodians and service providers. Recent bootcamps and important meetings with policy makers in Asia, Europe and Latin America reflect the network’s growing global presence.
This post Bitcoin Liquid Network Surpasses $3.27 Billion in Total Value Locked first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:44:16
@ 6d5c826a:4b27b659
2025-05-23 21:44:16- Atomia DNS - DNS management system.
ISCPerl - Designate - DNSaaS services for OpenStack. (Source Code)
Apache-2.0Python - DNSControl - Synchronize your DNS to multiple providers from a simple DSL. (Source Code)
MITGo/Docker - DomainMOD - Manage your domains and other internet assets in a central location. (Source Code)
GPL-3.0PHP - nsupdate.info - Dynamic DNS service. (Demo, Source Code)
BSD-3-ClausePython - octoDNS - DNS as code - Tools for managing DNS across multiple providers.
MITPython - Poweradmin - Web-based DNS control panel for PowerDNS server. (Source Code)
GPL-3.0PHP - SPF Toolbox - Application to look up DNS records such as SPF, MX, Whois, and more. (Source Code)
MITPHP
- Atomia DNS - DNS management system.
-
 @ eed7ca5d:191de8eb
2025-05-23 13:58:46
@ eed7ca5d:191de8eb
2025-05-23 13:58:46Growing up, we were told that in order to build wealth, we need to save little by little. By living below your means, you are providing more for your future.
It is a simple formula that will help you build up the capital necessary to buy a car, a house or start a business… You prioritize long-term benefits and delayed gratification over immediate rewards.
This is called having a low-time preference. In contrast, high-time preference individuals prioritize today over tomorrow, seeking immediate gratification.
Austrian economists explain that civilization growth is driven by low-time preference societies. Groups of individuals who prioritize long-term planning are able to innovate and develop new tools for a better future. Over time, this behavior leads to technological inventions like the light bulb and artistic masterpieces like the Notre Dame cathedral.
***What happens when you realize that the money you save is losing value over time? ***
There is less incentive to save for the future, because in the future your savings will be worth less. You might as well spend it now and enjoy life today.
When the money you save loses its value, you are facing one of two choices:
-
Spend it today and reap the rewards of your hard work;
-
Invest it (stocks, real estate, etc.) with the hope to reap higher rewards later, bearing the risk of losing it all if the investment does not pay off.
There is a distinct difference between saving and investing as the latter approach is riskier than the former. By investing, you are betting on the upside while bearing the downside risk. Saving, in contrast, comes without downside risk. That difference becomes blurry when the money you save is losing value. In fact, saving becomes inherently a losing approach. Logically, you will be forced to place a speculative bet with the hope to outperform the guaranteed loss of value. You are required to find a way to hedge your bet…
Humans over time have always sought out a medium to save their economic energy for a better future. That used to be beads and seashells, and evolved to precious metals like gold and silver.
Money is a tool that we use to save our economic energy over time, and exchange value with each other.
I spend time fishing, you spend time farming, the neighbor spends time building homes, and society rewards us with money for the time and energy we spent being productive
Today, the tool that we use to save our economic energy is clearly losing value over time. The nominal value remains the same, but the purchasing power is decreasing. In other words, the value of our time today will be worth less in the future.
That explains why everyone around us is looking for the next best investment opportunity. We are all needing to become investment experts, speculators, on top of our respective professions. Speculation became necessary, and some of us are forced into a high-time preference lifestyle.
Earn now and spend it all now before you lose it.
This should not be the case…
Time is Money
Our time is the only scarce resource we all have. We use it to be productive and generate economic value, then store that value in the form of money in order to reap the rewards in the future.
Money is the abstract representation of our time. Hence, time is money.
In January 2009, at the height of the global financial crisis, a software protocol called Bitcoin was released pseudonymously by Satoshi Nakamoto. This individual (or group) released a whitepaper a few months prior named “Bitcoin: A Peer-to-Peer Electronic Cash System” outlining how the system enables secure, peer-to-peer transactions without relying on a central authority. (https://bitcoin.org/bitcoin.pdf)
Although there are more technical concepts involved, the bitcoin protocol can be thought of as a language for communicating value. The same way we respect the rules of the English language to communicate ideas with one another, bitcoin users adhere to the network’s consensus rules to communicate value with each other in a peer-to-peer fashion.
There are no physical or digital coins in the bitcoin network. Rather, it is a collection of transactions transferring value from sender to recipient. Transactions are validated and propagated by nodes across the network, before being recorded into the blockchain. The Bitcoin blockchain is a global public ledger of all transactions that cannot be altered.
More importantly, Bitcoin is money that does not lose value overtime.
-
Its supply is capped at 21 million coins.
-
Its scarcity increases over time due to the predictable issuance rate, which halves roughly every 4 years.
-
Its decentralized nature puts the power in the hands of its users.
-
There is no governing body that can devalue or alter it.
It is a tool that we can use to save our economic energy over time, and be able to use it later.
It is the scarcest verifiable commodity: we cannot make more of it no matter how high its demand grows. That cannot be said for any other commodity in the world today.
A savings tool in disguise
See, most people tend to view bitcoin as another speculative investment. They presume they have missed out on another investment opportunity, and it’s now too late to get in.
Meanwhile, it is quite the opposite. Bitcoin’s value will keep growing over time due to its deflationary nature.
With bitcoin, we can save for a better future, for a rainy day, and spend more time with our loved ones or focusing on our craft to build better tools or artistic masterpieces. It takes away the burden of having to speculate on which stock will perform best, or which real estate market will grow the fastest, all while working one or multiple jobs
Bitcoin is not another investment opportunity you missed out on. It is the best savings tool humans have invented (or discovered), while everything else is the speculative bet. Bitcoin is the hedge against the guaranteed devaluation of money, without any counterparty risk.
What we were taught as children is true. With the right tool, the idea that saving will help you build wealth overtime stands true. Bitcoin might seem like an investment today given the volatility during its adoption phase. In reality, it is the perfect way to store your time and economic energy and grow your wealth. Whether you make $1/hour or $1M/hour, you can start saving in the best money humans have invented.
My goal is to help people around me understand this technology and break the stigma around it.
Bitcoin is not the next best investment.
It is the best tool we have found to store our economic energy across time and exchange value with each other.
Bitcoin is Money.
-
-
 @ ec9bd746:df11a9d0
2025-04-06 08:06:08
@ ec9bd746:df11a9d0
2025-04-06 08:06:08🌍 Time Window:
🕘 When: Every even week on Sunday at 9:00 PM CET
🗺️ Where: https://cornychat.com/eurocornStart: 21:00 CET (Prague, UTC+1)
End: approx. 02:00 CET (Prague, UTC+1, next day)
Duration: usually 5+ hours.| Region | Local Time Window | Convenience Level | |-----------------------------------------------------|--------------------------------------------|---------------------------------------------------------| | Europe (CET, Prague) 🇨🇿🇩🇪 | 21:00–02:00 CET | ✅ Very Good; evening & night | | East Coast North America (EST) 🇺🇸🇨🇦 | 15:00–20:00 EST | ✅ Very Good; afternoon & early evening | | West Coast North America (PST) 🇺🇸🇨🇦 | 12:00–17:00 PST | ✅ Very Good; midday & afternoon | | Central America (CST) 🇲🇽🇨🇷🇬🇹 | 14:00–19:00 CST | ✅ Very Good; afternoon & evening | | South America West (Peru/Colombia PET/COT) 🇵🇪🇨🇴 | 15:00–20:00 PET/COT | ✅ Very Good; afternoon & evening | | South America East (Brazil/Argentina/Chile, BRT/ART/CLST) 🇧🇷🇦🇷🇨🇱 | 17:00–22:00 BRT/ART/CLST | ✅ Very Good; early evening | | United Kingdom/Ireland (GMT) 🇬🇧🇮🇪 | 20:00–01:00 GMT | ✅ Very Good; evening hours (midnight convenient) | | Eastern Europe (EET) 🇷🇴🇬🇷🇺🇦 | 22:00–03:00 EET | ✅ Good; late evening & early night (slightly late) | | Africa (South Africa, SAST) 🇿🇦 | 22:00–03:00 SAST | ✅ Good; late evening & overnight (late-night common) | | New Zealand (NZDT) 🇳🇿 | 09:00–14:00 NZDT (next day) | ✅ Good; weekday morning & afternoon | | Australia (AEDT, Sydney) 🇦🇺 | 07:00–12:00 AEDT (next day) | ✅ Good; weekday morning to noon | | East Africa (Kenya, EAT) 🇰🇪 | 23:00–04:00 EAT | ⚠️ Slightly late (night hours; late night common) | | Russia (Moscow, MSK) 🇷🇺 | 23:00–04:00 MSK | ⚠️ Slightly late (join at start is fine, very late night) | | Middle East (UAE, GST) 🇦🇪🇴🇲 | 00:00–05:00 GST (next day) | ⚠️ Late night start (midnight & early morning, but shorter attendance plausible)| | Japan/Korea (JST/KST) 🇯🇵🇰🇷 | 05:00–10:00 JST/KST (next day) | ⚠️ Early; convenient joining from ~07:00 onwards possible | | China (Beijing, CST) 🇨🇳 | 04:00–09:00 CST (next day) | ❌ Challenging; very early morning start (better ~07:00 onwards) | | India (IST) 🇮🇳 | 01:30–06:30 IST (next day) | ❌ Very challenging; overnight timing typically difficult|
-
 @ 6d5c826a:4b27b659
2025-05-23 21:43:55
@ 6d5c826a:4b27b659
2025-05-23 21:43:55- Ceph - Distributed object, block, and file storage platform. (Source Code)
LGPL-3.0C++ - DRBD - Distributed replicated storage system, implemented as a Linux kernel driver. (Source Code)
GPL-2.0C - GlusterFS - Software-defined distributed storage that can scale to several petabytes, with interfaces for object, block and file storage. (Source Code)
GPL-2.0/LGPL-3.0C - Hadoop Distributed Filesystem (HDFS) - Distributed file system that provides high-throughput access to application data. (Source Code)
Apache-2.0Java - JuiceFS - Distributed POSIX file system built on top of Redis and S3. (Source Code)
Apache-2.0Go - Kubo - Implementation of IPFS, a global, versioned, peer-to-peer filesystem that seeks to connect all computing devices with the same system of files.
Apache-2.0/MITGo - LeoFS - Highly available, distributed, replicated eventually consistent object/blob store. (Source Code)
Apache-2.0Erlang - Lustre - Parallel distributed file system, generally used for large-scale cluster computing. (Source Code)
GPL-2.0C - Minio - High-performance, S3 compatible object store built for large scale AI/ML, data lake and database workloads. (Source Code)
AGPL-3.0Go - MooseFS - Fault tolerant, network distributed file system. (Source Code)
GPL-2.0C - OpenAFS - Distributed network file system with read-only replicas and multi-OS support. (Source Code)
IPL-1.0C - Openstack Swift - A highly available, distributed, eventually consistent object/blob store. (Source Code)
Apache-2.0Python - Perkeep - A set of open source formats, protocols, and software for modeling, storing, searching, sharing and synchronizing data (previously Camlistore). (Source Code)
Apache-2.0C - TahoeLAFS - Secure, decentralized, fault-tolerant, peer-to-peer distributed data store and distributed file system. (Source Code)
GPL-2.0Python - XtreemFS - Distributed, replicated and fault-tolerant file system for federated IT infrastructures.. (Source Code)
BSD-3-ClauseJava
- Ceph - Distributed object, block, and file storage platform. (Source Code)
-
 @ 47259076:570c98c4
2025-05-23 13:57:28
@ 47259076:570c98c4
2025-05-23 13:57:28"Know thyself and you will know the universe and the gods"
This is the greatest truth.
Knowing yourself is a process that is perhaps eternal.
Knowing yourself means making conscious what is unconscious, in all fields.
Making conscious your material reality, your emotions, your thoughts, your mind, your patterns, your spirit, your flaws, your qualities, etc.
The journey is within.
And in this process, burning everything that is not you.
Burning everything so only the essential remains.
The essential being your higher self.
You are not your body, you are not your emotions, you are not your mind, etc...
You are pure consciousness.
Everyday we can learn from him, but if we are asleep, we will not realize the gold opportunities passing right in front of our eyes.
Everyday he teaches us.
If everyday he teaches us, why stress so much for having an astral projection?
If an astral projection happens with you, it will be a good experience indeed, if you know how to value opportunities.
Otherwise, you may see some """evil"" spirits trying to scare you.
Therefore, don't depend on astral projection for your spiritual growth.
In fact, don't depend on anything.
Don't depend on books, don't depend on people, don't depend on "psychologists", don't depend on "rituals", don't depend on institutions, and of course, don't depend on the "government".
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:43:37
@ 6d5c826a:4b27b659
2025-05-23 21:43:37- Diagrams.net - A.K.A. Draw.io. Easy to use Diagram UI with a plethora of templates. (Source Code)
Apache-2.0JavaScript/Docker - Kroki - API for generating diagrams from textual descriptions. (Source Code)
MITJava - Mermaid - Javascript module with a unique, easy, shorthand syntax. Integrates into several other tools like Grafana. (Source Code)
MITNodejs/Docker
- Diagrams.net - A.K.A. Draw.io. Easy to use Diagram UI with a plethora of templates. (Source Code)
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-23 13:46:21
@ 5d4b6c8d:8a1c1ee3
2025-05-23 13:46:21You'd think I'd be most excited to talk about that awesome Pacers game, but, no. What I'm most excited about this week is that @grayruby wants to continue Beefing with Cowherd.
Still, I am excited to talk about Tyrese Haliburton becoming a legendary Knicks antagonist. Unfortunately, the Western Conference Finals are not as exciting. Also, why was the MVP announcement so dumb?
The T20k cricket contest is tightening up, as we head towards the finish. Can @Coinsreporter hold on to his vanishing lead?
@Carresan has launched Football Madness. Let's see if we understand whatever the hell this is any better than we did last week.
On this week's Blok'd Shots, we'll ridicule Canada for their disgraceful loss in the World Championships and talk about the very dominant American Florida Panthers, who are favorites to win the Stanley Cup.
Are the Colorado the worst team in MLB history?
The Tush Push has survived another season. Will the NFL eventually ban it or will teams adjust?
Plus, whatever else Stackers want to talk about.
https://stacker.news/items/987399
-
 @ 266815e0:6cd408a5
2025-04-04 07:54:02
@ 266815e0:6cd408a5
2025-04-04 07:54:02This should be published to nostr using nostr-connect account
-
 @ 30b99916:3cc6e3fe
2025-05-23 13:16:37
@ 30b99916:3cc6e3fe
2025-05-23 13:16:37sourcegraph #vibecoding #ai #bitcoin #security
After reading the article Revenge of the junior developer, this inspired me to go take a look at Sourcegraph.com to get a better understanding of all this AI stuff.
The first step was installing the VS Code extension called, Cody which is a coding agent. The Cody features explain the code in a file and review and analyze code did an extremely impressive job with VaultApi and BTCwallet.
VaultApi and BTCwallet are PowerShell scripts that are available from my BTCPAY Server
All of the following output was generated by Cody.
Code Analysis of VaultApi.ps1
The VaultApi.ps1 script is generally well-structured and follows many PowerShell best practices. It has comprehensive documentation, version history, and clear parameter definitions. The suggestions below would further enhance what is already a solid codebase. The author has clearly put significant effort into making the script functional and user-friendly, with good attention to cross-platform compatibility and security considerations.
VaultApi.ps1 Explanation
VaultApi.ps1 is a PowerShell script that helps users interact with HashiCorp Vault, which is a tool for securely storing and managing sensitive information like passwords and API keys.
Purpose of the Code
This script makes it easier to use Vault by providing simple commands to start the Vault server, unlock it (unseal), log in, store secrets, retrieve secrets, and shut down the server. Think of it as a friendly interface that simplifies all the complex operations you would otherwise need to do manually with Vault.
Inputs
The script takes several inputs:
- An
actionparameter that tells the script what operation to perform (like "Start", "Stop", "Kv1Create", "Kv1Read") - A
kvpathparameter that specifies where in Vault to store or retrieve information - A
kvalueparameter for the actual secret value you want to store - A
kvkeyparameter that lets you specify a custom name for your secret - Optional switches like
-Infoto show more detailed information and-Rawto display output directly instead of copying to clipboard
Outputs
Depending on the action performed, the script produces different outputs:
- Text messages in the console showing the status of operations
- Secret values retrieved from Vault (either displayed or copied to clipboard)
- Lists of available secret paths
- Status information about the Vault server
- Backup files of your Vault data
How It Works
The script works by:
- First checking if Vault is installed and running
- Setting up communication with the Vault server using its API address
- Performing the requested action by sending the appropriate commands to Vault
- Processing any responses and displaying results to the user
For example, when you use the "Kv1Create" action, the script:
- Checks if you're logged in
- Verifies the path doesn't already exist
- Formats your data correctly
- Sends a request to Vault to create the new secret
- Shows you the result
Important Logic Flows
Some key processes in the script include:
-
Authentication flow: The script helps you log in using either a token or username/password, then stores your authentication token for future commands.
-
Unsealing process: Vault requires multiple keys to unlock (unseal) it after starting. The script can retrieve these keys from a secure file or prompt you to enter them.
-
Secret management: The script handles creating, reading, updating, and deleting secrets, supporting both single values and multiple key-value pairs at a path.
-
Path management: The script can list all available paths and help you search for specific ones, making it easier to organize and find your secrets.
-
Value generation: When creating or updating secrets, you can use the keyword "setvalue" to automatically generate a random 20-character value, which is then copied to your clipboard.
The script uses a configuration file in your home directory to know how to connect to Vault, and it can optionally use encrypted files to store sensitive information like unlock keys. It communicates with Vault using REST API calls, which are like special messages that tell Vault what to do.
In summary, VaultApi.ps1 is a helper tool that makes it much easier to use HashiCorp Vault for securely storing and managing your sensitive information, without needing to remember all the complex commands and procedures.
Code Analysis of BTCwallet.ps1
The script generally follows sound design principles with good organization, comments, and documentation. It demonstrates thoughtful error checking and user interaction. The identified opportunities for enhancement would primarily improve security, maintainability, and robustness rather than addressing fundamental flaws. The script author has clearly put significant effort into creating a comprehensive tool with good documentation and practical functionality.
BTCwallet.ps1 Explanation
The BTCwallet.ps1 script is a PowerShell tool designed to help Bitcoin users manage different wallet applications on a Linux system. It provides a convenient way to start, stop, and check the status of Bitcoin wallets while adding security features.
Purpose
The main purpose of this script is to securely manage Bitcoin wallets, particularly focusing on "cold storage" solutions. Cold storage means keeping your Bitcoin wallet data in an encrypted container that's only mounted when needed, which is more secure than keeping it always accessible ("hot storage").
Inputs
The script takes one main input parameter:
$action: This can be "start", "stop", or "check" (default), telling the script what operation to perform on your Bitcoin wallet.
Outputs
The script doesn't return data but produces several visible outputs:
- Status messages showing whether wallets are running or stopped
- Prompts for user input when decisions are needed
- Confirmation messages when actions are completed
How It Works
-
When you run the script, it first loads a configuration file (BTCwalletCfg.xml) that contains information about which wallets you have installed.
-
Based on the
$actionparameter, it performs one of three main functions:- Check: Shows if your wallet application is currently running
- Start: Launches your wallet application, with options for hot or cold storage
- Stop: Closes your wallet application and securely dismounts any encrypted containers
- For security, the script can use HashiCorp Vault (a secure password manager) to store sensitive information like passwords for encrypted containers.
-
The script also verifies its own integrity by checking its file hash against a previously stored value, alerting you if the script has been modified.
Important Logic Flows
Starting a Wallet
When starting a wallet, the script:
- Asks which wallet you want to use (Sparrow, GreenWallet, or Wasabi)
- Checks if HashiCorp Vault is running and starts it if needed
- Verifies the script's integrity by comparing file hashes
- Asks if you want to use hot or cold storage
- For cold storage, it:
- Retrieves the encrypted container's location and password
- Mounts the encrypted container using VeraCrypt
- Starts the wallet application pointing to the mounted container
- For hot storage, it simply starts the wallet application with default settings
Stopping a Wallet
When stopping a wallet, the script:
- Checks if the wallet is still running and asks you to close it first if needed
- For cold storage wallets, it moves any wallet files back to the encrypted container
- Dismounts the encrypted container
- Optionally stops the HashiCorp Vault service
The script handles different wallet applications (Sparrow, GreenWallet, and Wasabi) slightly differently based on how each one stores its data and what command-line options they support.
In summary, BTCwallet.ps1 provides a secure way to manage Bitcoin wallets by combining wallet applications with encrypted storage and password management, all controlled through simple commands.
- An
-
 @ 6d5c826a:4b27b659
2025-05-23 21:43:11
@ 6d5c826a:4b27b659
2025-05-23 21:43:11- Capistrano - Deploy your application to any number of machines simultaneously, in sequence or as a rolling set via SSH (rake based). (Source Code)
MITRuby - CloudSlang - Flow-based orchestration tool for managing deployed applications, with Docker capabilities. (Source Code)
Apache-2.0Java - CloudStack - Cloud computing software for creating, managing, and deploying infrastructure cloud services. (Source Code)
Apache-2.0Java/Python - Cobbler - Cobbler is a Linux installation server that allows for rapid setup of network installation environments. (Source Code)
GPL-2.0Python - Fabric - Python library and cli tool for streamlining the use of SSH for application deployment or systems administration tasks. (Source Code)
BSD-2-ClausePython - Genesis - A template framework for multi-environment BOSH deployments.
MITPerl - munki - Webserver-based repository of packages and package metadata, that allows macOS administrators to manage software installs. (Source Code)
Apache-2.0Python - Overcast - Deploy VMs across different cloud providers, and run commands and scripts across any or all of them in parallel via SSH. (Source Code)
MITNodejs
- Capistrano - Deploy your application to any number of machines simultaneously, in sequence or as a rolling set via SSH (rake based). (Source Code)