-
 @ eb0157af:77ab6c55
2025-05-28 07:01:26
@ eb0157af:77ab6c55
2025-05-28 07:01:26Bitcoin surpasses gold in the United States: 50 million holders and a dominant role in the global market.
According to a new report by River, for the first time in history, the number of Americans owning bitcoin has surpassed that of gold holders. The analysis reveals that approximately 50 million U.S. citizens currently own the cryptocurrency, while gold owners number 37 million. In fact, 14.3% of Americans own bitcoin, the highest percentage of holders worldwide.

Source: River
The report highlights that 40% of all Bitcoin-focused companies are based in the United States, consolidating America’s dominant position in the sector. Additionally, 40.5% of Bitcoin holders are men aged 31 to 35, followed by 35.9% of men aged 41 to 45. In contrast, only 13.4% of holders are women.

Source: River
Notably, U.S. companies hold 94.8% of all bitcoins owned by publicly traded companies worldwide. According to the report, recent regulatory changes in the U.S. have made the asset more accessible through financial products such as spot ETFs.
The document also shows that American investors increasingly view the cryptocurrency as protection against fiscal instability and inflation, appreciating its limited supply and decentralized governance model.
For River, Bitcoin offers significant practical advantages over gold in the modern digital era. Its ease of custody, cross-border transfer, and liquidity make the cryptocurrency an attractive option for both individual and institutional investors, the report suggests.
The post USA: 50 million Americans own bitcoin appeared first on Atlas21.
-
 @ eb0157af:77ab6c55
2025-05-27 07:01:37
@ eb0157af:77ab6c55
2025-05-27 07:01:37The exchange reveals the extent of the breach that occurred last December as federal authorities investigate the data leak.
Coinbase has disclosed that the personal data of 69,461 users was compromised during the breach in December 2024, according to documentation filed with the Maine Attorney General’s Office.
The disclosure comes after Coinbase announced last week that a group of hackers had demanded a $20 million ransom, threatening to publish the stolen data on the dark web. The attackers allegedly bribed overseas customer service agents to extract information from the company’s systems.
Coinbase had previously stated that the breach affected less than 1% of its user base, compromising KYC (Know Your Customer) data such as names, addresses, and email addresses. In a filing with the U.S. Securities and Exchange Commission (SEC), the company clarified that passwords, private keys, and user funds were not affected.
Following the reports, the SEC has reportedly opened an official investigation to verify whether Coinbase may have inflated user metrics ahead of its 2021 IPO. Separately, the Department of Justice is investigating the breach at Coinbase’s request, according to CEO Brian Armstrong.
Meanwhile, Coinbase has faced criticism for its delayed response to the data breach. Michael Arrington, founder of TechCrunch, stated that the stolen data could cause irreparable harm. In a post on X, Arrington wrote:
“The human cost, denominated in misery, is much larger than the $400m or so they think it will actually cost the company to reimburse people. The consequences to companies who do not adequately protect their customer information should include, without limitation, prison time for executives.”
Coinbase estimates the incident could cost between $180 million and $400 million in remediation expenses and customer reimbursements.
Arrington also condemned KYC laws as ineffective and dangerous, calling on both regulators and companies to better protect user data:
“Combining these KYC laws with corporate profit maximization and lax laws on penalties for hacks like these means these issues will continue to happen. Both governments and corporations need to step up to stop this. As I said, the cost can only be measured in human suffering.”
The post Coinbase: 69,461 users affected by December 2024 data breach appeared first on Atlas21.
-
 @ 21335073:a244b1ad
2025-05-21 16:58:36
@ 21335073:a244b1ad
2025-05-21 16:58:36The other day, I had the privilege of sitting down with one of my favorite living artists. Our conversation was so captivating that I felt compelled to share it. I’m leaving his name out for privacy.
Since our last meeting, I’d watched a documentary about his life, one he’d helped create. I told him how much I admired his openness in it. There’s something strange about knowing intimate details of someone’s life when they know so little about yours—it’s almost like I knew him too well for the kind of relationship we have.
He paused, then said quietly, with a shy grin, that watching the documentary made him realize how “odd and eccentric” he is. I laughed and told him he’s probably the sanest person I know. Because he’s lived fully, chasing love, passion, and purpose with hardly any regrets. He’s truly lived.
Today, I turn 44, and I’ll admit I’m a bit eccentric myself. I think I came into the world this way. I’ve made mistakes along the way, but I carry few regrets. Every misstep taught me something. And as I age, I’m not interested in blending in with the world—I’ll probably just lean further into my own brand of “weird.” I want to live life to the brim. The older I get, the more I see that the “normal” folks often seem less grounded than the eccentric artists who dare to live boldly. Life’s too short to just exist, actually live.
I’m not saying to be strange just for the sake of it. But I’ve seen what the crowd celebrates, and I’m not impressed. Forge your own path, even if it feels lonely or unpopular at times.
It’s easy to scroll through the news and feel discouraged. But actually, this is one of the most incredible times to be alive! I wake up every day grateful to be here, now. The future is bursting with possibility—I can feel it.
So, to my fellow weirdos on nostr: stay bold. Keep dreaming, keep pushing, no matter what’s trending. Stay wild enough to believe in a free internet for all. Freedom is radical—hold it tight. Live with the soul of an artist and the grit of a fighter. Thanks for inspiring me and so many others to keep hoping. Thank you all for making the last year of my life so special.
-
 @ 51bbb15e:b77a2290
2025-05-21 00:24:36
@ 51bbb15e:b77a2290
2025-05-21 00:24:36Yeah, I’m sure everything in the file is legit. 👍 Let’s review the guard witness testimony…Oh wait, they weren’t at their posts despite 24/7 survellience instructions after another Epstein “suicide” attempt two weeks earlier. Well, at least the video of the suicide is in the file? Oh wait, a techical glitch. Damn those coincidences!
At this point, the Trump administration has zero credibility with me on anything related to the Epstein case and his clients. I still suspect the administration is using the Epstein files as leverage to keep a lot of RINOs in line, whereas they’d be sabotaging his agenda at every turn otherwise. However, I just don’t believe in ends-justify-the-means thinking. It’s led almost all of DC to toss out every bit of the values they might once have had.
-
 @ 99e7936f:d5d2197c
2025-05-28 14:55:40
@ 99e7936f:d5d2197c
2025-05-28 14:55:40“Dieser Beitrag wurde mit dem Pareto-Client geschrieben.”
Wo bleibt die Rettung?
Wenn man bei einem Notfall auf den Rettungswagen wartet, dann fühlen sich Minuten wie Stunden an. Die Nerven sind bis zum Anschlag gespannt, alle Sinne sind geschärft.
Die Natur hat das so eingerichtet, damit man aufmerksam und gut geschützt ist vor weiteren Verletzungen.
Bei Trauma ist das auch so, nur dass dieser Zustand gefühlt ein halbes Leben andauert. Das klingt brutal, ist aber in etwa so. Da ein menschlicher Körper das nicht gut aushalten kann, sendet er dem Gehirn die Information: “ Bitte mach etwas zur Entlastung, ich kann mit dem Dauerstress nicht gut umgehen. Ich habe ständig das Gefühl, dass etwas Schlimmes passiert und ich mich verteidigen muss.“ Das Gehirn überlegt sich dann eine Lösung, um auch selber endlich wieder Ruhe zu haben. In der Regel wird der traumatische Inhalt verdrängt, vergessen, abgewandelt, abgeschwächt oder als Schwarz-Weiß-Film wieder gegeben, also ohne Gefühl (re)präsentiert. Man kann dann von den traumatischen Erlebnissen erzählen, ohne ein einziges Gefühl zu haben. Das wirkt souverän, als habe man das Trauma verarbeitet, das Gegenteil ist der Fall. Manche Menschen reden sogar über Gefühle, empfinden diese aber nicht. Gefühle werden imitiert oder inszeniert. Wenn man selber fühlen kann, spürt man diesen feinen Unterschied als Zuhörer sofort. Jedenfalls ist alles das Traumafolge bzw. die Lösung, die uns das Gehirn nach Trauma anbietet. Entweder ist der ganze Inhalt samt Emotion weg, oder der Inhalt ist noch da, aber die Emotion dazu fehlt. Es gibt Menschen, die so tief traumatisiert sind, dass sie eine ganz andere Geschichte von sich selbst erzählen, als die, die eigentlich stattgefunden hat. Ich weiß, dass das gruselig klingt. Aber das ist eine Realität. Und es ist vermutlich gut so. Die Natur macht alles, um ein Menschenleben zu retten, und wenn es um den Preis des psychologischen Vergessens ist. Manche Erinnerungen sind offensichtlich nicht mit dem Leben vereinbar, deswegen werden sie für immer abgespalten. Mittlerweile habe ich persönlich viel Respekt vor Menschen, die sich an nichts mehr „erinnern“ können, da ich gelernt habe, dass sie am schlimmsten traumatisiert sind. Diese Einstellung hatte ich nicht immer.
Jedenfalls verhält es sich nach meiner Beobachtung und auch nach meinen eigenen Erfahrungen so, dass man sich ganz oft erst dann vollständig UND in Farbe an traumatische Erlebnisse erinnert, wenn die Zeit dafür reif ist. Man könnte auch sagen, wenn die Seele bereit ist, die verlorenen Seelenanteile wieder zuzulassen. Sie sind nie weg, denn eine unsichtbare Schnur verbindet uns immer mit dem, was passiert ist. Also, wenn dieser Moment, in dem Du Deine Seelenanteile wieder begrüßen darfst, kommt, dann ist das wie ein riesiges Geschenk, auch wenn sich das zu Beginn nicht so anfühlt. Es fühlt sich dann eher so an, wie wenn man auf den Rettungswagen wartet, aber es ist definitiv ein Geschenk, genau wie eine Geburt ein Geschenk ist. Und eine Geburt ist ja auch nicht immer leicht.
Also, je mehr Gefühl beim Erinnern von traumatischen Inhalten spürbar ist, desto besser kann Traumabearbeitung gelingen. (Heiße den Schmerz willkommen, wenn er in Dein Leben kommt.) Ich persönlich hatte lange Wehen, bevor mein Trauma dann schlagartig aktiviert wurde. Das war, bildlich gesprochen, eine Hausgeburt, die ich allein vollbracht habe, weil der Rettungswagen dermaßen Verspätung hatte. Aber das Kind hat sich dennoch gut entwickelt. Ich habe zuvor lange von meinem Trauma „nur“ geredet. Ich habe rationalisiert, wie man in der Fachsprache sagt. Mir war meine frühe Verletzung bewusst, aber ich hatte kein Gefühl zu dem, was ich erlebt hatte. Als das Gefühl da war, verstand ich, dass es sinnvoll war, es solange nicht gefühlt haben zu können, denn es war ein überwältigender Schmerz. Die Natur macht instinktiv ein gutes Timing für die Wiederkehr des Gefühls. Sie sucht sich eine Zeit im Leben aus, wo man einen guten Stand hat, stabil ist, eine Umgebung hat, die einen zumindest für eine Weile halten und auffangen kann. Denn die Natur möchte schließlich, dass man auch die Wiederkehr des Gefühls überlebt.
Genauso schmerzhaft wie der Verlust des Gefühls war, genauso schmerzhaft ist seine Wiederkehr.
Der Schmerz ist quasi der Erste und der Letzte. Er macht das Licht aus, und später macht er das Licht oder den Farbfilm wieder an. Der Schmerz ist viel besser als sein Ruf.
Ich erzähle hier lediglich meine Erfahrungen und Beobachtungen, auch wenn ich allgemein formuliere. Das kann sich bei anderen Menschen auch anders verhalten. Aber ich finde den Erfahrungsaustausch über dieses Thema wichtig, WEIL es unterschiedlich sein kann und jeder auf einem anderen Level von Traumabearbeitung steht. Ein Problem bei Traumabearbeitung ist, dass jeder ein anderes Trauma erlebt hat, dass jeder einen anderen Nährboden hatte, auf den das Trauma fiel, und dass es verschiedene Stadien gibt, bis es dann endlich und hoffentlich soweit ist, dass das Trauma wieder vollständig in die eigene Psyche integriert werden kann und man wieder „ganz“ bzw. „neu und etwas anders“ ist. Und meine Erfahrung ist, dass man auf das Tempo dieses Prozesses leider keinen Einfluss hat, auch wenn es hierzu, wie ich finde, viele falsche Verkehrsdurchsagen gibt. Die Natur ist da verschlossen wie eine Auster, sie lässt sich nicht ins Handwerk pfuschen. Als ich das verstand, hat sich mein Wunsch, Menschen zu helfen, schlagartig verändert. Ich verstand, dass ICH das nicht machen kann, dass die Natur das selber macht. Und das ist eine gute Nachricht, denn die Natur kann das am besten und ist ein super zuverlässiger Partner.
Wir brauchen keinen Rettungswagen. Der Schmerz ist die Rettung.
Das Thema „Trauma“ birgt so viel positiven Erkenntnisgewinn über das Wunder des Lebens.
Aber zurück zum Thema. Wenn man, so wie ich, ein halbes Leben in einem Schwarz-Weiß-Film verbracht hat, dann die Hausgeburt ohne Rettungswagen durchgestanden hat und das Kind irgendwann anfängt, neugierige Fragen zu stellen, dann ist man im Zugzwang. In dieser Situation bin ich heute. Deswegen schreibe ich. Mein neues ICH fragt mich immer öfter, warum ich so viele Dinge tue, die ich eigentlich gar nicht mehr tun will. Kinder fragen einen auch manchmal ganz unverblümt, ob man den Hansi denn lieb hat oder ob man gerne im Büro arbeitet. Wenn man den Hansi nicht lieb hat und nicht gerne im Büro arbeitet, dann muss man schlucken und eine kindgerechte Antwort formulieren. Genauso wenig wie Kinder als kompetenter 20-jähriger auf die Welt kommen, genau so wenig ist man nach geglückter Traumabearbeitung „geheilt“. Es wird nichts schlagartig besser. Das ist auch so eine falsche Verkehrsdurchsage. Man lebt ja noch im alten Leben, was nun Schritt für Schritt verändert werden darf. ABER man ist glückliche Mutter. Mutter sein, ist nicht immer leicht, habe ich mir sagen lassen. Mütter lieben ihre Kinder. Im Idealfall machen sie sich keine Gedanken darüber, was aus ihrem Kind mal werden soll. Sie vertrauen einfach darauf, DASS aus ihrem Kind ein glücklicher Mensch wird und buttern deshalb so viel Liebe in das Kind hinein, wie in den wenigen Jahren, die das Kind ein Kind ist, möglich ist. So ähnlich geht es mir heute auch. Ich bin stolz auf mein neues ICH und lobe es, so oft ich kann. Jede Mutter lobt ihre Butter. Das ist wichtig, denn das Leben bietet ständig Herausforderungen, an denen man bekanntlich wachsen darf. Ich gehe jeden Tag mit meinem „Kind“ spazieren, und wir sehen viel. Wir sehen andere Menschen mit Trauma, wir hören zu, welches Trauma der andere erlebt hat und auf welchem Level er ist. Wir hören das Gefühl heraus, welches mitschwingt. Wir sehen Menschen in ihrem Schwarz-Weiß-Film. Und wir sehen Menschen, die scheinbar mit jeder Situation souverän umgehen können. Am meisten interessieren „uns“ zur Zeit solche Menschen, die ehrlich zugeben, dass sie Wehen haben, dass der Schmerz sich in immer kürzeren Abständen meldet. (Die verlorenen Seelenanteile ziehen an der unsichtbaren Schnur.) Mit diesen Leuten kann ich im Moment am besten. Das hört sich komisch an. Aber ich will damit zum Ausdruck bringen, dass ich mit diesen Menschen mittlerweile am meisten resoniere. Sie sprechen meine Sprache. Sie empfinden Gefühle, und sprechen über diese. Das ist für mich die schönste Sprache.
Wer in diesen Tagen wahrhaftig Schmerz empfindet, und nicht nur als Lippenbekenntnis, sondern echten üblen Schmerz über die enttäuschte Liebe oder über die Verhältnisse in dieser Welt, der ist mir sympathisch, der ist mir nah. Denn ich weiß, dass so ein fühlender Mensch auch bald eine Niederkunft erleben wird, die ihn verändert, die ihn anders auf diese Welt schauen lässt.
Der Schmerz bringt uns die Verwandlung. Der Schmerz bringt die verlorenen Seelenanteile zurück. Der Schmerz ist der Hüter des Lebens. Der Schmerz bringt Dir Deine volle Sensibilität für andere Menschen zurück. Alles, was Du bei Dir nicht fühlen kannst, kannst Du bei anderen nicht fühlen. Der Schmerz beendet das. Er macht das Licht an und gibt dem Film wieder Farbe.
Heiße den Schmerz willkommen, wenn er in Dein Leben kommt. Tu das, nicht etwa weil Du gern leidest, nein tu das, weil Du Dich liebst, weil Du bewusst darauf achten möchtest, was Dir wirklich gut tut und Freude macht. Ein Mensch oder ein Job, der Dir Schmerz bereitet, den gilt es loszulassen. Und wenn Du Schmerz im Gesicht Deines Gegenübers siehst, dann frage Dich ehrlich, was Dein Anteil daran ist, dass der andere leidet. Wir sind nicht für jedes Leid auf dieser Welt verantwortlich, das möchte ich hier auch betonen. Und die Schuld-Nummer zieht bei mir schon lange nicht mehr. Aber ich nehme immer besser wahr, wenn mein eigenes Verhalten nicht angemessen, nicht authentisch ist, von überholten Glaubensmustern geprägt ist. Ich kann das erkennen und korrigieren. Ich kann das heute selber erkennen, weil der Schmerz mich das gelehrt hat, mich geöffnet hat. Der Schmerz lehrt uns ganz viel. Der Schmerz ist der Hüter des Lebens. Er trifft einen hart, macht aber weich.
Heiße den Schmerz willkommen, denn er ist die Rettung.
“Dieser Beitrag wurde mit dem Pareto-Client geschrieben.”
Onboarding bei Nostr: Nostr
Easy onboarding via **Start.**\ \ Das Pareto-Team baut den “Marktplatz der Ideen” und hat dabei schon viel erreicht. \ team@pareto.space \ https://pareto.space \ https://geyser.fund/project/pareto?hero=1c1b8e487090
\ \ Newsletter per Mail (Die Friedenstaube)\ hier abonnieren\ \ In Telegram lesen -> hier unsere Kanäle\ https://t.me/pareto_artikel \ https://t.me/friedenstaube_artikel \ \ Als Feed in einem Feed-Reader \ https://pareto.space/atom/feed.xml \ https://pareto.space/atom/de_feed.xml \ https://pareto.space/atom/en_feed.xml
-
 @ c9badfea:610f861a
2025-05-20 19:49:20
@ c9badfea:610f861a
2025-05-20 19:49:20- Install Sky Map (it's free and open source)
- Launch the app and tap Accept, then tap OK
- When asked to access the device's location, tap While Using The App
- Tap somewhere on the screen to activate the menu, then tap ⁝ and select Settings
- Disable Send Usage Statistics
- Return to the main screen and enjoy stargazing!
ℹ️ Use the 🔍 icon in the upper toolbar to search for a specific celestial body, or tap the 👁️ icon to activate night mode
-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ c1e9ab3a:9cb56b43
2025-05-27 16:19:06
@ c1e9ab3a:9cb56b43
2025-05-27 16:19:06Star Wars is often viewed as a myth of rebellion, freedom, and resistance to tyranny. The iconography—scrappy rebels, totalitarian stormtroopers, lone smugglers—suggests a deep anti-authoritarian ethos. Yet, beneath the surface, the narrative arc of Star Wars consistently affirms the necessity, even sanctity, of central authority. This blog entry introduces the question: Is Star Wars fundamentally a celebration of statism?
Rebellion as Restoration, Not Revolution
The Rebel Alliance’s mission is not to dismantle centralized power, but to restore the Galactic Republic—a bureaucratic, centrally governed institution. Characters like Mon Mothma and Bail Organa are high-ranking senators, not populist revolutionaries. The goal is to remove the corrupt Empire and reinstall a previous central authority, presumed to be just.
- Rebels are loyalists to a prior state structure.
- Power is not questioned, only who wields it.
Jedi as Centralized Moral Elites
The Jedi, often idealized as protectors of peace, are unelected, extra-legal enforcers of moral and military order. Their authority stems from esoteric metaphysical abilities rather than democratic legitimacy.
- They answer only to their internal Council.
- They are deployed by the Senate, but act independently of civil law.
- Their collapse is depicted as tragic not because they were unaccountable, but because they were betrayed.
This positions them as a theocratic elite, not spiritual anarchists.
Chaos and the Frontier: The Case of the Cantina
The Mos Eisley cantina, often viewed as a symbol of frontier freedom, reveals something darker. It is: - Lawless - Violent - Culturally fragmented
Conflict resolution occurs through murder, not mediation. Obi-Wan slices off a limb; Han shoots first—both without legal consequence. There is no evidence of property rights, dispute resolution, or voluntary order.
This is not libertarian pluralism—it’s moral entropy. The message: without centralized governance, barbarism reigns.
The Mythic Arc: Restoration of the Just State
Every trilogy in the saga returns to a single theme: the fall and redemption of legitimate authority.
- Prequels: Republic collapses into tyranny.
- Originals: Rebels fight to restore legitimate order.
- Sequels: Weak governance leads to resurgence of authoritarianism; heroes must reestablish moral centralism.
The story is not anti-state—it’s anti-bad state. The solution is never decentralization; it’s the return of the right ruler or order.
Conclusion: The Hidden Statism of a Rebel Myth
Star Wars wears the costume of rebellion, but tells the story of centralized salvation. It: - Validates elite moral authority (Jedi) - Romanticizes restoration of fallen governments (Republic) - Portrays decentralized zones as corrupt and savage (outer rim worlds)
It is not an anarchist parable, nor a libertarian fable. It is a statist mythology, clothed in the spectacle of rebellion. Its core message is not that power should be abolished, but that power belongs to the virtuous few.
Question to Consider:
If the Star Wars universe consistently affirms the need for centralized moral and political authority, should we continue to see it as a myth of freedom? Or is it time to recognize it as a narrative of benevolent empire? -
 @ a39d19ec:3d88f61e
2025-04-22 12:44:42
@ a39d19ec:3d88f61e
2025-04-22 12:44:42Die Debatte um Migration, Grenzsicherung und Abschiebungen wird in Deutschland meist emotional geführt. Wer fordert, dass illegale Einwanderer abgeschoben werden, sieht sich nicht selten dem Vorwurf des Rassismus ausgesetzt. Doch dieser Vorwurf ist nicht nur sachlich unbegründet, sondern verkehrt die Realität ins Gegenteil: Tatsächlich sind es gerade diejenigen, die hinter jeder Forderung nach Rechtssicherheit eine rassistische Motivation vermuten, die selbst in erster Linie nach Hautfarbe, Herkunft oder Nationalität urteilen.
Das Recht steht über Emotionen
Deutschland ist ein Rechtsstaat. Das bedeutet, dass Regeln nicht nach Bauchgefühl oder politischer Stimmungslage ausgelegt werden können, sondern auf klaren gesetzlichen Grundlagen beruhen müssen. Einer dieser Grundsätze ist in Artikel 16a des Grundgesetzes verankert. Dort heißt es:
„Auf Absatz 1 [Asylrecht] kann sich nicht berufen, wer aus einem Mitgliedstaat der Europäischen Gemeinschaften oder aus einem anderen Drittstaat einreist, in dem die Anwendung des Abkommens über die Rechtsstellung der Flüchtlinge und der Europäischen Menschenrechtskonvention sichergestellt ist.“
Das bedeutet, dass jeder, der über sichere Drittstaaten nach Deutschland einreist, keinen Anspruch auf Asyl hat. Wer dennoch bleibt, hält sich illegal im Land auf und unterliegt den geltenden Regelungen zur Rückführung. Die Forderung nach Abschiebungen ist daher nichts anderes als die Forderung nach der Einhaltung von Recht und Gesetz.
Die Umkehrung des Rassismusbegriffs
Wer einerseits behauptet, dass das deutsche Asyl- und Aufenthaltsrecht strikt durchgesetzt werden soll, und andererseits nicht nach Herkunft oder Hautfarbe unterscheidet, handelt wertneutral. Diejenigen jedoch, die in einer solchen Forderung nach Rechtsstaatlichkeit einen rassistischen Unterton sehen, projizieren ihre eigenen Denkmuster auf andere: Sie unterstellen, dass die Debatte ausschließlich entlang ethnischer, rassistischer oder nationaler Kriterien geführt wird – und genau das ist eine rassistische Denkweise.
Jemand, der illegale Einwanderung kritisiert, tut dies nicht, weil ihn die Herkunft der Menschen interessiert, sondern weil er den Rechtsstaat respektiert. Hingegen erkennt jemand, der hinter dieser Kritik Rassismus wittert, offenbar in erster Linie die „Rasse“ oder Herkunft der betreffenden Personen und reduziert sie darauf.
Finanzielle Belastung statt ideologischer Debatte
Neben der rechtlichen gibt es auch eine ökonomische Komponente. Der deutsche Wohlfahrtsstaat basiert auf einem Solidarprinzip: Die Bürger zahlen in das System ein, um sich gegenseitig in schwierigen Zeiten zu unterstützen. Dieser Wohlstand wurde über Generationen hinweg von denjenigen erarbeitet, die hier seit langem leben. Die Priorität liegt daher darauf, die vorhandenen Mittel zuerst unter denjenigen zu verteilen, die durch Steuern, Sozialabgaben und Arbeit zum Erhalt dieses Systems beitragen – nicht unter denen, die sich durch illegale Einreise und fehlende wirtschaftliche Eigenleistung in das System begeben.
Das ist keine ideologische Frage, sondern eine rein wirtschaftliche Abwägung. Ein Sozialsystem kann nur dann nachhaltig funktionieren, wenn es nicht unbegrenzt belastet wird. Würde Deutschland keine klaren Regeln zur Einwanderung und Abschiebung haben, würde dies unweigerlich zur Überlastung des Sozialstaates führen – mit negativen Konsequenzen für alle.
Sozialpatriotismus
Ein weiterer wichtiger Aspekt ist der Schutz der Arbeitsleistung jener Generationen, die Deutschland nach dem Zweiten Weltkrieg mühsam wieder aufgebaut haben. Während oft betont wird, dass die Deutschen moralisch kein Erbe aus der Zeit vor 1945 beanspruchen dürfen – außer der Verantwortung für den Holocaust –, ist es umso bedeutsamer, das neue Erbe nach 1945 zu respektieren, das auf Fleiß, Disziplin und harter Arbeit beruht. Der Wiederaufbau war eine kollektive Leistung deutscher Menschen, deren Früchte nicht bedenkenlos verteilt werden dürfen, sondern vorrangig denjenigen zugutekommen sollten, die dieses Fundament mitgeschaffen oder es über Generationen mitgetragen haben.
Rechtstaatlichkeit ist nicht verhandelbar
Wer sich für eine konsequente Abschiebepraxis ausspricht, tut dies nicht aus rassistischen Motiven, sondern aus Respekt vor der Rechtsstaatlichkeit und den wirtschaftlichen Grundlagen des Landes. Der Vorwurf des Rassismus in diesem Kontext ist daher nicht nur falsch, sondern entlarvt eine selektive Wahrnehmung nach rassistischen Merkmalen bei denjenigen, die ihn erheben.
-
 @ d360efec:14907b5f
2025-05-27 15:46:26
@ d360efec:14907b5f
2025-05-27 15:46:26 -
 @ 9e9085e9:2056af17
2025-05-28 15:21:58
@ 9e9085e9:2056af17
2025-05-28 15:21:58Part 3: Features That Can Drive User Engagement
Growing the Yakihonne Community – What’s Next?
To attract more users and keep engagement high, Yakihonne could expand with the following features:
- Gamification & Milestones
Badges, activity points, and rewards to motivate interaction.
- Smart Content Discovery
Trending topics, hashtag feeds, and AI-curated (but private) suggestions.
- Community Tools
Verified groups, decentralized moderation, and event features.
- Rich Profile Customization
Bio, themes, badges, and follower highlights.
- Lightning Micro-Tipping
Enable users to send instant tips for posts or engagement.
- Cross-Device Compatibility
Smooth use across mobile, web, and desktop.
- Developer Ecosystem
Open APIs to allow third-party apps and tools to thrive.
Yakihonne #Yakihonne #Yakihonne #Nostr #Nostr #YoungDfx
-
 @ 3bf0c63f:aefa459d
2025-05-28 15:06:06
@ 3bf0c63f:aefa459d
2025-05-28 15:06:06Keys are meaningless
A common misconception of technologists when they first discover Nostr is to put too much weight on the cryptography and start worshipping the keypairs.
Secret keys are just numbers. To some people this will sound amazing, but in fact it is just a little boring. Numbers by themselves don't do anything. A simple computer script can generate a bazillion keys with no effort at all: but does that have any effect in the world? No.
The key-focused approach to Nostr is responsible for well-known slogans such as "not your keys, not your notes" or "self-sovereign identity". But these are meaningless slogans, and not only because people are not keys, but because these keys don't do anything without the means of actual action in the world.
Is a person locked in a cage "free"? If you use the key-worshipper logic then yes. That locked person is the only one who can move their own body or think their own thoughts, in the same sense that a person with a secret key is the only one who can sign things using that key (obviously). Both are "self-sovereign", blablabla.
The point is that "sovereignty" (what an unfortunate word) is meaningless if the person cannot leave the cage and do more interesting things in the world. In the same sense having a key is meaningless if you cannot publish messages to where the people you're trying to reach can read them.
-
 @ d360efec:14907b5f
2025-05-27 15:45:21
@ d360efec:14907b5f
2025-05-27 15:45:21 -
 @ 3bf0c63f:aefa459d
2025-05-28 15:06:06
@ 3bf0c63f:aefa459d
2025-05-28 15:06:06Nostr is pro-censorship
In Keys are meaningless we hopefully made it clear that keys are not central to Nostr's idea, in fact keys are just an unnecessary burden that enables something much more important: relays.
The fact that one user, through their client, can reach out to a huge number of these servers hosted anywhere, and that each user can publish their stuff to any of them, from a modest server at his basement to a big cloud relay hosted by a big company, without anyone having to trust any of these: this is the core of the Nostr idea.
And the fact that Nostr relies on an open ecosystem of privately-owned relay servers is the only thing that ensures a proper incentive structure and gives it a chance of working: while other centralized platforms and protocols in the past -- even those that have tried to be very open and anti-censorship -- ended up struggling against what whom or what should be allowed to be published or not -- because after all they relied on a big common "global" pool of messages that had to be interpreted by apps.
That reliance kills the entire idea because at the very least someone has to host the content, and hosting that content has a cost, it has moral implications and also legal implications, so at some point someone, somewhere, has to make a decision to stop hosting some things, or restricting some users from publishing and so on, and there will never be a global agreement between all the peoples of the Earth about whom or what should be allowed and what should be disallowed. Even a rate-limit, IP blocking or other naïve measures that a server must necessarily take in order to survive on the internet, are a form of "censorship".
On Nostr none of that is a factor because each relay is independent of each other and there is no global pool of content, by definition. Because of that, and because it's the job of the readers to figure out from where to read, no relay has any obligations to please all the peoples of the Earth and is free to impose any limits or policies it wants.
Of course all of that breaks down if apps relinquish their obligation to figure out what relays to read from and decide to read from a static list of relays, but that should have gone without saying.
See also
-
 @ 8d34bd24:414be32b
2025-05-28 13:53:46
@ 8d34bd24:414be32b
2025-05-28 13:53:46These days it can feel like the whole world is out of control. Government officials lie and break the law. People are selfish, act emotionally rather than logically, and push ideologies that are illogical and contrary to reality. Society is divided into groups and people are judged, not for their own character, but based on which group they are placed into. There are wars and rumors of wars. There are worries of pandemics and economic disasters. Depression, psychosis, and despair is rampant even among the youngest among us.
Hope For Believers
As much as things seem to be out of control, they are not out of God’s control. This is what the Bible predicted. No matter how bad things get in the world, those who have put their faith in Jesus, do not need to feel despair.
Why are you in despair, O my soul?\ And why have you become disturbed within me?\ Hope in God, for I shall again praise Him\ For the help of His presence.\ O my God, my soul is in despair within me;\ Therefore I remember You from the land of the Jordan\ And the peaks of Hermon, from Mount Mizar. (Psalm 42:5-6)
When we start to feel despair overcoming us, we need to remember what God has done and what He has promised. We need to praise God for what He has done, what He has promised, and what He will bring to completion. Things may be hard now, but God is still in control, and we know how the story will end. God triumphs. Good is rewarded. Evil is destroyed. We can stand on the foundation of hope because we know the ending. Even though things may be out of our personal control, they are always under God’s control.
The more fiercely the storm rages, the more we need to rest in Jesus and the more we need to put our hope in Him.
O love the Lord, all you His godly ones!\ The Lord preserves the faithful\ And fully recompenses the proud doer.\ **Be strong and let your heart take courage,\ All you who hope in the Lord. (Psalm 31:23-24) {emphasis mine}
We can take courage because God always acts for our long term good. Every hardship we experience here on earth will be recognized as a blessing that grew our faith and prepared us for heaven and God’s presence in eternity.
For I know the plans that I have for you,’ declares the Lord, ‘plans for welfare and not for calamity to give you a future and a hope. (Jeremiah 29:11)
Even the worst things that happen to us, due to the sins of others, have a good purpose in our lives. God is working good through us. Our hope isn’t an empty hope. It isn’t a “I really hope this happens.” It is a “I can hope in the guaranteed promises of God.”
For we do not want you to be unaware, brethren, of our affliction which came to us in Asia, that we were burdened excessively, beyond our strength, so that we despaired even of life; indeed, we had the sentence of death within ourselves so that we would not trust in ourselves, but in God who raises the dead; who delivered us from so great a peril of death, and will deliver us, He on whom we have set our hope. And He will yet deliver us, (2 Corinthians 1:8-10) {emphasis mine}
We may experience situations so bad that they seem hopeless, but with God, nothing is hopeless. The God who raises the dead can raise us out of any situation. The God who spoke the universe into existence can deliver us by a word.
The God of the Bible knows all and loves us completely. He looks at our situation through the lens of eternity. What seems best in the moment is not necessarily what is best for our eternity. Many times He delivers us through hardship rather than out of it. We just need to trust Him and put our hope in Him because He is good.
In the same way God, desiring even more to show to the heirs of the promise the unchangeableness of His purpose, interposed with an oath, so that by two unchangeable things in which it is impossible for God to lie, we who have taken refuge would have strong encouragement to take hold of the hope set before us. This hope we have as an anchor of the soul, a hope both sure and steadfast and one which enters within the veil, where Jesus has entered as a forerunner for us, having become a high priest forever according to the order of Melchizedek. (Hebrews 6:17-20) {emphasis mine}
Read that statement again. “This hope we have as an anchor of the soul, a hope both sure and steadfast.” Are you trusting Jesus as the “anchor of your soul?” Is your hope just a wish or is it a “sure and steadfast” hope based on the promises of God that you know will 100% come true?
And not only this, but we also exult in our tribulations, knowing that tribulation brings about perseverance; and perseverance, proven character; and proven character, hope; and hope does not disappoint, because the love of God has been poured out within our hearts through the Holy Spirit who was given to us. (Romans 5:3-5)
Isn’t it ironic that we need hope to persevere through tribulations, but that persevering through tribulation gives us character and hope? Our faith, trust, and hope grow through hardship. When things are easy, we almost always fall back on trusting in our own power rather than relying on God’s power. If we have put our faith in Jesus, there is no situation in which we should lose hope.
Now may the God of hope fill you with all joy and peace in believing, so that you will abound in hope by the power of the Holy Spirit. (Romans 15:13)
Is your joy and peace based on your circumstances or have you learned to have hope in God so you can experience joy and peace even in the trials?
Many people equate joy and happiness, but I think there is a key distinction. Happiness is a pleasant feeling that comes from pleasant circumstances. Joy is a similar feeling to happiness, but it comes from knowing God and His love. It is not tied to circumstances. When we have truly put our hope in God we can still have joy in and despite the most horrific circumstances.
Blessed be the God and Father of our Lord Jesus Christ, who according to His great mercy has caused us to be born again to a living hope through the resurrection of Jesus Christ from the dead, to obtain an inheritance which is imperishable and undefiled and will not fade away, reserved in heaven for you, (1 Peter 1:3-4) {emphasis mine}
Just as Jesus told the Samaritan woman at the well that He provides living water that wells up inside, so that she need never thirst, in the same way believers have a living hope that wells up in times of need. Our hope is in the Creator of the universe and Savior of the world. No problem is too big for Him. No situation is a surprise to Him. No enemy is too powerful for Him. All of our problems are already solved. We just haven’t necessarily seen the solution yet.
My soul, wait in silence for God only,\ For my hope is from Him.\ He only is my rock and my salvation,\ My stronghold; I shall not be shaken.\ On God my salvation and my glory rest;\ The rock of my strength, my refuge is in God. (Psalm 62:5-7)
Despair For Unbelievers
Although believers never have reason to despair, the same is not true for those who have rejected the Savior, Jesus Christ. In these perilous times, they have a real reason for dread and despair.
Moreover, the Lord will scatter you among all peoples, from one end of the earth to the other end of the earth; and there you shall serve other gods, wood and stone, which you or your fathers have not known. Among those nations you shall find no rest, and there will be no resting place for the sole of your foot; but there the Lord will give you a trembling heart, failing of eyes, and despair of soul. So your life shall hang in doubt before you; and you will be in dread night and day, and shall have no assurance of your life. (Deuteronomy 64-66)
Those who reject the atoning sacrifice of Jesus do not get His protection. They do not get His help. They cannot rest in hope in Him.
Of course, the good news is that they can chose to turn their hearts to Him, confess their sins, and trust in Him up until their moment of death. Sadly many will continue to put off faith until it is too late. Many will choose evil over good and license over submission until God gives them over to their lusts.
And just as they did not see fit to acknowledge God any longer, God gave them over to a depraved mind, to do those things which are not proper, being filled with all unrighteousness, wickedness, greed, evil; full of envy, murder, strife, deceit, malice; they are gossips, slanderers, haters of God, insolent, arrogant, boastful, inventors of evil, disobedient to parents, without understanding, untrustworthy, unloving, unmerciful; and although they know the ordinance of God, that those who practice such things are worthy of death, they not only do the same, but also give hearty approval to those who practice them. (Romans 1:28-32)
If any of you have not yet put your trust in Jesus as Savior and Lord, do not wait. Turn away from evil. Submit to the will of Jesus. Trust Him to take away your sins and cover you with His righteousness.
If any of you know people who are in despair, share the gospel with them. Tell them about the greatness of God. Show them the hope that is within you.
Can Believers Despair?
Are there believers who despair? Yes. Should believers ever despair? Definitely not!
But we have this treasure in earthen vessels, so that the surpassing greatness of the power will be of God and not from ourselves; we are afflicted in every way, but not crushed; perplexed, but not despairing; persecuted, but not forsaken; struck down, but not destroyed; always carrying about in the body the dying of Jesus, so that the life of Jesus also may be manifested in our body. (2 Corinthians 4:7-10)
Jesus is always with believers in all situations guiding and protecting us. Those difficult situations that happen are for our good, even when we can’t see how it could be for good.
Job had more reasons to despair than almost anyone, yet he trusted in God. He didn’t know why he was being put through such loss, but his loss increased his faith in God and was a great example to people throughout history. I also love this cry of his heart.
“Oh that my words were written!\ Oh that they were inscribed in a book!” (Job 19:23)
He may or may not have seen even the partial fulfillment of this cry, but His words are written in the book of Job, in the Holy Scriptures read by Jews and Christians throughout the world and throughout history. Job’s first response to loss was an example to us all. After losing all ten children and all of his wealth, this was his response.
Then Job arose and tore his robe and shaved his head, and he fell to the ground and worshiped. (Job 1:20)
Yes, it is true that he had moments of despair where he cursed his birth, but he then returned to God in faith and hope. After a brief rebuke from God, Job submitted to God’s will.
“Behold, I am insignificant; what can I reply to You?\ I lay my hand on my mouth.\ Once I have spoken, and I will not answer;\ Even twice, and I will add nothing more.” (Job 40:4-5)
After his second rebuke from God, he fully submitted.
Then Job answered the Lord and said,
“I know that You can do all things,\ And that no purpose of Yours can be thwarted.\ ‘Who is this that hides counsel without knowledge?’\ *Therefore I have declared that which I did not understand,\ Things too wonderful for me, which I did not know.\ ‘Hear, now, and I will speak;\ I will ask You, and You instruct me*.’\ I have heard of You by the hearing of the ear;\ But now my eye sees You;\ Therefore I retract,\ And I repent in dust and ashes**.” (Job 42:1-6) {emphasis mine}
Job admitted that he did not understand what God was doing, but that God was right; God was good; and God was Lord. Job was able to have hope knowing that God was in control and working for good.
In the case of Job, he was later blessed with more kids, more wealth, and more respect than he had in the beginning. We won’t all see our blessings here on earth, but all believers will receive blessings from their trials.
May our glorious Savior and God fill you with faith and hope in God, His goodness, His power, and His plan. May we all submit to His good will even when we do not understand and even when every part of our earthly body is crying, “stop!” May God fill you with knowledge of Him, faith in Him, and hope in Him.
Trust Jesus
-
 @ a39d19ec:3d88f61e
2025-03-18 17:16:50
@ a39d19ec:3d88f61e
2025-03-18 17:16:50Nun da das deutsche Bundesregime den Ruin Deutschlands beschlossen hat, der sehr wahrscheinlich mit dem Werkzeug des Geld druckens "finanziert" wird, kamen mir so viele Gedanken zur Geldmengenausweitung, dass ich diese für einmal niedergeschrieben habe.
Die Ausweitung der Geldmenge führt aus klassischer wirtschaftlicher Sicht immer zu Preissteigerungen, weil mehr Geld im Umlauf auf eine begrenzte Menge an Gütern trifft. Dies lässt sich in mehreren Schritten analysieren:
1. Quantitätstheorie des Geldes
Die klassische Gleichung der Quantitätstheorie des Geldes lautet:
M • V = P • Y
wobei:
- M die Geldmenge ist,
- V die Umlaufgeschwindigkeit des Geldes,
- P das Preisniveau,
- Y die reale Wirtschaftsleistung (BIP).Wenn M steigt und V sowie Y konstant bleiben, muss P steigen – also Inflation entstehen.
2. Gütermenge bleibt begrenzt
Die Menge an real produzierten Gütern und Dienstleistungen wächst meist nur langsam im Vergleich zur Ausweitung der Geldmenge. Wenn die Geldmenge schneller steigt als die Produktionsgütermenge, führt dies dazu, dass mehr Geld für die gleiche Menge an Waren zur Verfügung steht – die Preise steigen.
3. Erwartungseffekte und Spekulation
Wenn Unternehmen und Haushalte erwarten, dass mehr Geld im Umlauf ist, da eine zentrale Planung es so wollte, können sie steigende Preise antizipieren. Unternehmen erhöhen ihre Preise vorab, und Arbeitnehmer fordern höhere Löhne. Dies kann eine sich selbst verstärkende Spirale auslösen.
4. Internationale Perspektive
Eine erhöhte Geldmenge kann die Währung abwerten, wenn andere Länder ihre Geldpolitik stabil halten. Eine schwächere Währung macht Importe teurer, was wiederum Preissteigerungen antreibt.
5. Kritik an der reinen Geldmengen-Theorie
Der Vollständigkeit halber muss erwähnt werden, dass die meisten modernen Ökonomen im Staatsauftrag argumentieren, dass Inflation nicht nur von der Geldmenge abhängt, sondern auch von der Nachfrage nach Geld (z. B. in einer Wirtschaftskrise). Dennoch zeigt die historische Erfahrung, dass eine unkontrollierte Geldmengenausweitung langfristig immer zu Preissteigerungen führt, wie etwa in der Hyperinflation der Weimarer Republik oder in Simbabwe.
-
 @ 629c4a12:f822cc1a
2025-02-23 21:33:31
@ 629c4a12:f822cc1a
2025-02-23 21:33:31I’ve always been drawn to minimalism. There’s a certain peace that comes from stripping away the unnecessary, decluttering both physical and mental spaces. Yet, when it comes to finances, I’ve found myself tangled in complexity. As an ‘optimizer,’ I spend an inordinate amount of time thinking about investments, managing risk, and endlessly tinkering with my portfolio. This preoccupation contradicts the minimalist principles I try to live by.
It seems absurd to me that the financial world has become so complicated that we need money managers to simply preserve the value of our money. If investing is so intricate that the average person must hire professionals just to preserve (let alone grow) the value of their savings, then something is fundamentally wrong.
For the past five years, I’ve immersed myself in the history and mechanics of financial systems. The deeper I delved, the clearer it became: Bitcoin is a force of minimalism in an increasingly financialized and complex world.
The Clutter of Modern Finance
Our financial system has become bloated with complexity. The hyper-securitization of assets has created an environment filled with financial clutter. Derivatives, for example, represent layers upon layers of financial engineering, often so convoluted that even experts struggle to understand them fully.
More troubling is the way nearly everything of value has been financialized. Real estate and art, two things that should embody personal value and cultural significance, have been transformed into mere asset classes. They are bought, sold, and speculated upon not for their intrinsic qualities but as instruments in the game of wealth preservation.
But why has this happened? It’s actually quite simple: our money is constantly losing value. The dollar, for example, debases at a rate of around 7% per year. Holding cash feels like holding melting ice, so it’s only natural for people to seek out scarce assets to preserve their wealth. The Never-Ending Game of Diversification
This pursuit of scarce assets sets off a complex game—a game that forces people to diversify endlessly:
- Equities
- Bonds
- Real Estate
- Commodities
- Art
- Collectibles
We’re told to spread our investments across these asset classes to mitigate risk and preserve our hard-earned money. Those who can afford to hire money managers generally fare better in this game, as they have access to expertise and strategies designed to navigate this maze of complexity.
Ironically, this system creates an incentive for more complexity. The more convoluted the financial landscape becomes, the more we need money managers, and the more entrenched this cycle of financialization and securitization becomes. It’s a force of ever-increasing entropy—quite the opposite of minimalism.
Bitcoin: Simplicity in a Complex World
In the midst of this financial chaos, Bitcoin emerges as a beacon of simplicity. It offers a way out of the clutter, a chance to reclaim financial minimalism. Bitcoin embodies the concept of scarcity with a rare kind of perfection: there will only ever be 21 million Bitcoins. No more.
This scarcity makes Bitcoin the perfect savings technology. Unlike traditional currencies, no one can debase your holdings. You don’t need to chase after real estate, art, or other assets to preserve your wealth. You don’t need to constantly diversify and rebalance a portfolio to stay ahead of inflation. Bitcoin’s scarcity gives you a way to hold your wealth securely, without the need for endless tinkering.
I’m not blind to Bitcoin’s short-term price volatility. However, it’s crucial to understand that we’re still in the early stages of adoption. As more people embrace this perfect form of scarcity, Bitcoin’s qualities as savings technology will express itself.
Bitcoin has the potential to de-financialize the housing market. It can de-financialize art.
Ultimately, Bitcoin has the power to replace those aspects of our lives that currently serve as proxies for scarcity.
A Minimalist Approach to Wealth
Bitcoin allows us to step off the treadmill of constant financial optimization. It offers a simpler way to safeguard the fruits of our labor. Rather than spending our time, energy, and attention on navigating a complex financial system, we can focus on what truly matters: living a meaningful life.
By embracing Bitcoin, we embrace a minimalist approach to wealth. We reject the idea that we must play a never-ending game of diversification to maintain our standard of living. Instead, we adopt a simple, elegant solution that aligns with the principles of minimalism.
Conclusion
In a world that grows more financially cluttered by the day, Bitcoin stands as a path to financial minimalism. It frees us from the complexities of traditional finance, allowing us to preserve our wealth without the need for constant vigilance and management.
By embodying scarcity and simplicity, Bitcoin gives us a way to reclaim our time and energy. It’s not just a financial tool; it’s a way to simplify our lives, to step back from the chaos, and to focus on what truly matters
-
 @ a29cfc65:484fac9c
2025-05-28 10:30:32
@ a29cfc65:484fac9c
2025-05-28 10:30:32Deutschland ist eines der wenigen Länder mit einer gesetzlich verankerten ausnahmslosen Schulbesuchspflicht. Mit den Schulschließungen in der Corona-Zeit wurde das Gesetz jedoch faktisch plötzlich außer Kraft gesetzt. Alle mussten zu Hause lernen. Als die Schulen danach wieder offen waren, wurden die Kinder mit Maskenpflicht, Tests und Impfdruck gequält. Nicht selten traten bei den Schülern Krankheiten und psychische Störungen auf. Nicht wenige Eltern suchten im Gespräch mit dem Lehrerkollegium nach Lösungen für ihre Kinder. In den meisten Fällen war das nicht möglich. Die Lehrer waren auf die neue Ideologie und die Durchsetzung der Maßnahmen eingeschworen und hatten Angst. Einige Eltern haben ihre Kinder dann in eigener Verantwortung aus der Schule genommen und zu Hause selbst unterrichtet. An manchen Orten fanden sich Gemeinschaften, wo die Kinder in Gruppen lernten. Während viele Lerngemeinschaften nicht mehr existieren, hat die Familie von Katharina den Unterricht für ihre drei Kinder in Eigenregie etabliert. Inzwischen haben sie dafür sogar „den Segen“ von Familiengericht und Jugendamt.
Katharina und Johannes leben mit ihren drei Wunschkindern Aurelius (15), Benjamin (14) und Friedrich (10) in einem Vorort von Leipzig. Die Familie wohnte früher in der Stadt. In der Corona-Zeit haben sie sich mit dem Physiotherapie- & Seminarzentrum Curasanus eine Existenz auf dem Land aufgebaut und begehen diesen Sommer ihr 20-jähriges Praxis-Jubiläum. Katharina hat ihre Arbeit als Physiotherapeutin weitgehend aufgegeben, um sich als Mama und Lernbegleiterin ihren Kindern widmen zu können. Daneben bietet sie Vorträge und Workshops an, übernimmt einen großen Teil der Praxis-Organisation und ist Manager, Rezeptionistin und Vertriebler der eigenen Firma. Wir besuchten einen ihrer Lachyoga-Kurse. Dabei erlebten wir ihr Zusammenspiel mit den drei Kindern. Anschließend stellten wir Katharina unsere Fragen zum Freilernen.
Im unmittelbaren Umfeld wird die Familie bestaunt und geachtet. Sie haben sich bewusst für das Freilernen entschieden. Die Kinder wurden ohne Test nicht mehr in die Schule gelassen. Auch andere Zwangsmaßnahmen wie die Maske wollten die Eltern den Kindern ersparen. Besonders Benjamin hatte traumatische Erlebnisse. Seine Lehrerin schmiss mit dem Schlüssel nach den Schülern und wandte andere schwarze Pädagogik an. Er ging ständig mit Bauchschmerzen ins Bett. Ein weiterer Punkt ist die Masernimpfung. Die Kinder könnten zwar zur Schule gehen, aber die Eltern werden mit rechtlichen Maßnahmen und Zwangszahlungen belegt. Da Katharina in ihrer Praxis viele Erkrankungen als Folge der Masernimpfung beobachten konnte, lehnt sie die Pflichtimpfung ab. Die Eltern haben kein Vertrauen mehr in die staatliche Schulerziehung mit all dem Zwang und den Erpressungen. Als die Familie den Entschluss gefasst hatte, die Kinder nicht mehr in die Schule zu schicken, haben sie ihre Praxis vorübergehend geschlossen, ihr Haus verkauft und sind auf Reisen gegangen. Die beiden großen Kinder wurden von der Schule abgemeldet. Nach der Rückkehr haben sie dann mit einem neuen Leben auf dem Land begonnen.
Lernen ohne Schule: Wie geht das?
„Wissen ist Macht und eine Holschuld“, sagt uns Katharina. Das ist ihr Motto und motiviert auch die Kinder. Mit dem Unterricht zu Hause macht die Familie ihre eigene Studie und zeigt, dass Lernen auch anders geht als in der Schule. Die Eltern können viel besser auf jedes einzelne Kind eingehen. Johannes arbeitete früher als Straßenbauer. Er unterstützt die Jungs vor allem in Mathematik, Geometrie und Physik sowie bei handwerklichen Fertigkeiten. Katharinas Stärken liegen in Deutsch, Sprachen und Organisation. Unter den Patienten ihrer Praxis gibt es Lehrer, die ihnen helfen. Weitere Unterstützung kommt von Freunden und Bekannten. Bei bestimmten Projekten treffen sie auf andere Freilernerkinder. „Das Netzwerk wird immer größer, es wird immer schöner und interessanter“, sagt Katharina. Man geht mit vielen anderen einen gemeinsamen Weg, verlässt dabei eingetretene Pfade und erkundet neue Themenfelder wie Mediengestaltung, freie Energie, Elektrotherapie, meditatives und Improvisations-Zeichnen. „Ich sprudele vor Ideen. Sie kommen in mein Feld, und dann mache ich was draus“, sagt Katharina. Die Jungs sind in Wurzen im Ringelnatz-Literaturkreis. Dort schreiben sie Drehbuchgeschichten und haben einen Film produziert. Sie suchen sich Projekte oder kreieren neue, wie mit dem Planetarium Eilenburg. Diese Zusammenarbeit hat sich sehr gut entwickelt. Dort lernen 4- bis 15-Jährige zusammen. Die drei Jungs spielen Klavier. Erdkunde und Geschichte erleben die Kinder auch dadurch, dass die Familie Hauptstädte oder die bosnischen Pyramiden selbst erkundet. Dabei erweist es sich als Vorteil, nicht auf die Ferienzeiten angewiesen zu sein.
Als Physiotherapeutin ist Katharina bewusst, dass man neue Lernstrategien entwickeln muss. Die Kinder lernen unterschiedlich. Jedes Kind hat seinen eigenen Charakter. Aurelius benötigt eher eine 1:1-Betreuung. Darauf kann Katharina viel individueller eingehen als die staatliche Schule. Es ist aber auch aufwendiger und anstrengender. Besonderen Wert legt sie darauf, dass rechte und linke Gehirnhälfte gleichmäßig beansprucht werden. Lernphasen werden immer wieder mit Entspannungs- oder Bewegungsphasen kombiniert. Sie weiß, dass den Kindern zuerst die Grundlagen des Lesens, Rechnens und Schreibens vermittelt werden müssen. Dann sind sie in der Lage, sich alles Weitere selbst anzueignen – Unterstützung vorausgesetzt. „Besonders das Schreiben mit der eigenen Hand ist wichtig für die Vernetzung der beiden Gehirnhälften“, sagt Katharina. Dafür nehmen sich die Eltern Zeit. Die Kinder führen Tagebuch. Außerdem halten es die Eltern für wichtig, den Kindern Werte und Tugenden wie Dankbarkeit, Verlässlichkeit, Beharrlichkeit, Aufrichtigkeit, Ehrlichkeit und die zehn Gebote zu vermitteln. Katharina und Johannes sind beide religiös begleitet aufgewachsen. Heute sehen sie die Kirche als Institution kritisch. Angebunden an die Schöpfung und im Gottvertrauen erschaffen und schöpfen sie Leben und Lebensraum aus eigener Kraft – so erklärt es uns Katharina.
Ein weiteres Thema sind die Funktionen des Körpers und wie sich die Kinder gesund erhalten können. Vieles lernen sie dabei in der Physiotherapiepraxis. Die Familie hat das Privileg, in ihrem eigenen Biorhythmus leben zu können. „Das macht sehr viel aus – wir sind alle gesund“, sagt Katharina. Der Lern- und Arbeitstag beginnt nicht vor 9 Uhr und hat eine eigene Struktur. Im Tagesablauf sind feste Verantwortlichkeiten integriert. So wechseln sich die Kinder aller drei Tage mit Tischdecken, Staubsaugen und Geschirrspüler ab. Das hilft ihnen, sich selbst zu organisieren. Das geht nicht immer reibungslos vonstatten. Wenn das Lernpensum beizeiten abgearbeitet wurde, helfen die Kinder im Haushalt oder Garten oder gehen ihrem Bewegungsdrang auf andere Weise nach. Die Eltern sind am Abend noch länger aktiv, denn die Praxis erfordert noch die eine oder andere bürokratische Pflicht. Die Familie ist sehr naturverbunden. Sie gehen viel in den Wald und in den Garten. Sie bauen selbst Gemüse und Obst an. Dabei können die Kinder zum Beispiel Erfahrungen mit Permakultur und natürlicher Düngung sammeln. Die Familie achtet auf die Ernährung, schließlich ist Katharina seit fast 25 Jahren Ernährungsberaterin. Was sie nicht selbst anbauen, wird beim Bauern des Vertrauens eingekauft. Die Jungs können selbst kochen und backen. Die Schädlichkeit von Zucker ist den Kindern schon bewusst geworden, ohne gänzlich auf Schokolade verzichten zu müssen. Medikamente gibt es im Haushalt nicht. Sie kennen sich sehr gut mit den Heilmitteln aus der Natur aus und können so ihre Selbstheilungskräfte aktivieren. Sie haben keinen Hausarzt. Natürlich hat keines der Kinder ein Handy. Bisher haben sie noch kein Verlangen danach. Die Eltern halten es für wichtig, dass die Kinder erst sicher bei Selbstorganisation und Tagesstruktur sind, bevor sie ein Handy bekommen. Katharina weist darauf hin, dass beispielsweise WhatsApp erst ab 16 Jahren zugelassen ist, und fragt sich, ob das andere Eltern wissen.
Gesetze auf Augenhöhe auslegen
Den Behörden blieben die Freilerner nicht verborgen. Sie wurden aktiv und schalteten das Familiengericht ein. Die Familie hatte keinen Anwalt und keine Rechtsschutzversicherung. Katharina erzählt uns, dass sie schließlich auf „Hilfe von oben“ gehofft habe. Irgendwer hat sie anscheinend erhört, denn sie bekamen „einen Engel“ als Verfahrensbeistand. Die Behörden waren sehr zugänglich. In den Gesprächen gab man zu, mit der Schulsituation ebenfalls nicht zufrieden zu sein. „Wir wollen so wie ihr, dass sich etwas verändert. Wir sind an Eurer Seite.“ Die Gespräche mit dem Jugendamt und der Richterin vom Familiengericht Grimma waren immer auf Augenhöhe. Schließlich legte man der Familie keine Steine in den Weg. Damit kann Katharina ihr Konzept nach außen leben und andere inspirieren. Ihre Schlussfolgerung: Eltern müssen sich ihrer Stärken bewusst werden und aus ihrer Angst herauskommen. Das Konzept muss aber zur Familie passen, denn jede Familie ist anders.
Die Basis für freies Lernen ist das Vertrauen der Eltern in ihre Kinder. Denn Kinder sind von Natur aus wissbegierig und wollen lernen. Katharina hat viel von Bertrand Stern und von Riccardo Leppe gelernt. Beiden wurde von ihren Eltern das Lernen ohne Schulbesuch ermöglicht. Mit Bertrand Stern hat Katharina Kontakt. Er wird im November am Buß- und Bettag eine kleine Fortbildung im Therapie- und Seminarzentrum geben. Für den Vorabend ist ein Vortrag geplant. Katharina zitiert Riccardo Leppe: „Es ändert sich nur was, wenn man es selbst tut.“ Er sei sich sicher, dass der Fortschritt beim Freilernen inzwischen so weit ist, dass „die Paste nicht wieder zurück in die Tube geht“.
Der Übergang zur Berufsausbildung
Die ersten Freilernerkinder kommen jetzt in das Alter, in dem sie eine Berufsausbildung beginnen können. Aurelius und Benjamin, die beiden „Großen“, machen seit Anfang des Jahres schon erste Praktika bei ortsansässigen Handwerksbetrieben. Beide Seiten sind sehr zufrieden. Durch die Praktika, die länger dauern als im schulischen Lehrplan vorgesehen, können sich die Kinder ausprobieren. Katharina findet es interessant miterleben zu dürfen, wie auf ihre Kinder reagiert wird. Bringen sie etwas mit, das die anderen nicht haben? Denken sie anders mit? Benjamin bekam schon ein Angebot, in einem Metallbau-Betrieb stundenweise mitzuarbeiten. In den Betrieben weiß man, dass die Abschlüsse der staatlichen Schulen größtenteils das Papier nicht wert sind, auf dem sie stehen. Viele verlassen die Schule und können kaum lesen und schreiben, von Selbstorganisation ganz zu schweigen. Ein Freilerner kann eine staatliche Externen-Prüfung ablegen, um einen Haupt- oder Realschulabschluss zu erwerben. Katharina: „Für eine Ausbildung bei einem privaten Unternehmer braucht man das nicht, allein der Unternehmer entscheidet über die Aufnahme des Auszubildenden“. Außerdem stehen den jungen Leuten Privatschulen oder der zweite Bildungsweg zur Verfügung. Wenn man einen praktischen Beruf ergreift, ist es immer noch möglich, sich bis zur Hochschulreife weiterzubilden. Nach mehrjährigen Tätigkeiten kann man bei den Kammern von Industrie, Handel und Handwerk (IHK und HWK) eine Abschlussprüfung ablegen, mit der man zum Studium zugelassen werden kann. Oder man geht gleich den Weg in die Selbstständigkeit.
Frei lernen weitergedacht
Während der Coronazeit haben sich in Sachsen und speziell um Leipzig herum kleine Freilernergruppen gefunden. Die Gruppen werden aktuell zusammengeführt, um zum Beispiel gemeinsam den Mathematikunterricht zu gestalten. Besonders um Dresden herum ist die Szene noch stärker ausgeprägt. Außerdem gibt es seit mehr als 20 Jahren den Bundesverband Natürlich Lernen (BVNL). Er bietet Beratung und zentrale Veranstaltungen an.
Der Wunsch nach dem freien Lernen ohne Schulzwang ist groß. Doch die meisten Eltern wollen ihre Kinder dafür irgendwo abgeben und nicht selbst unterrichten. Katharinas größter Wunsch ist es, drei bis fünf Elternpaare zu finden, die sich in die Betreuung und Unterrichtung ihrer Kinder teilen. Das größte Hindernis dafür sieht sie in den Eltern selbst. Durch ungelöste transgenerative Konflikte und unverarbeitete Familientraumata kommen sie noch nicht in ihre eigene Kraft für ein selbstbestimmtes Leben. Viele wagen es noch nicht, ihre Erwerbstätigkeit zugunsten der Kinder einzuschränken. Katharina sieht es als große Aufgabe für sich und ihre Familie, mit dem Freilernen das Gemeinschaftsbewusstsein und gute Konfliktlösungsstrategien zu entwickeln. Sie denkt dabei bereits an ihre Enkel. Aber sie weiß auch, dass die Eltern ein sehr hohes Maß an Eigeninitiative, Motivation und Selbstdisziplin aufbringen müssen. Sie würde Eltern, die sich das noch nicht zutrauen, als Traumabegleiterin zur Verfügung stehen, für einen angemessenen Energieausgleich. Diese gegenseitige Unterstützung käme Kindern und Eltern zugute. Ebenso hält sie die Idee der Mehrgenerationenerziehung für wichtig. Dabei profitieren nicht nur die Kinder. Die Erfahrungen der älteren Menschen gehen nicht verloren, sondern werden an die jüngeren Generationen weitergegeben und machen sie resilienter. Das hilft den Eltern, ihrer Erwerbsarbeit nachzugehen und Familientraumata zu bewältigen.
Katharina ist eine starke Frau und sprüht nur so vor Energie. Selbst als wir nach 21 Uhr das Therapiezentrum verlassen, sind ihr die Anstrengungen des Tages nicht anzumerken. Sie wird nicht müde beim Sprechen. Für Fragen zum Thema Freilernen kann man sich an sie wenden.
Der Text wurde zuerst am 27.05.2025 im Blog „Freie Akademie für Medien und Journalismus“ veröffentlicht (https://www.freie-medienakademie.de/medien-plus/lernen-neu-gemacht)
Bildquelle: Salah Darwish, unsplash.com
-
 @ 1c19eb1a:e22fb0bc
2025-05-08 21:55:46
@ 1c19eb1a:e22fb0bc
2025-05-08 21:55:46If you haven't noticed already, #Nostr is a little different from what most people are used to. One of the ways this is felt most acutely is with media hosting. Users are accustomed to uploading their images and videos directly through the app they are posting from. Many Nostr apps provide that same experience nowadays, but it wasn't always the case.
Just a couple years ago, users had to find somewhere to host their media separately, and then copy and paste the URL into their note whenever they wanted to share their cat pictures. One of the first, if not the first, media hosting services specifically intended for Nostr was nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7, which will be the service we are reviewing today.
Like our previous review of Amber, Nostr.Build is a service for users to pair with other Nostr apps. You won't generally use nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 by itself. Rather, you'll use it to host that incredible shot you want to post to #Olas, or to host screenshots for your long-form tutorial about setting up Nostr Wallet Connect that you'll be posting from #Habla.news, or for hosting a hilarious video of your cat falling asleep to nostr:npub1cj8znuztfqkvq89pl8hceph0svvvqk0qay6nydgk9uyq7fhpfsgsqwrz4u's voice and taking a tumble off of his favorite perch that you want to share on #Damus. However, there are some features within Nostr.Build that you may want to check out quite apart from using it with any other Nostr app.
Overall Impression
Score: 4.8 / 5
I have been impressed by Nostr.Build for some time now, but they have pulled out all the stops in their latest update, increasing their maximum file size for free accounts to 100MB, integrating the #Blossom protocol, adding the ability to share directly to Nostr from within your dashboard, and more integrations with other Nostr apps than ever before. Nostr.Build is simply a pleasure to use, whether through their web interface, or through another Nostr app that integrates with them.
With the ability to easily organize your media, view statistics, browse the media gallery of free uploads, metadata removal for increased privacy, and AI image generation, Nostr.Build is not simply a media hosting service, it is a full-fledged media management platform. Its robust features keep it well ahead of other Nostr-focused media hosting options available, and a particularly strong option for those using Blossom and wanting redundancy and reliable uptime for their media.
As much as I enjoy using the web interface, though, where Nostr.Build really shines is their integrations with other Nostr apps. These integrations allow users to have the same experience they are accustomed to from centralized social platforms of uploading their media from within the same app they are using to share it. No copy/pasting a URL from one app to another. In fact, many users may not realize they have been using Nostr.Build in their client of choice, simply because it is the default option for media hosting for many Nostr apps.
This has the added benefit to client developers that they can provide this experience to their users without having to run media hosting infrastructure on top of trying to build their app. The separation of relays, clients, and media hosting between different entities, while keeping a similar experience to centralized platforms where a single company controls all three, is critical to Nostr adoption.
Features
Nostr.Build has a plethora of features beyond simply hosting your media. Let's take a look!
AI Image Generation
Do you need a quick title image for a long-form article? How about inspiration for a logo or art piece? Nostr.Build's AI Studio has you covered.
They have provided a few different models based on the plan you purchase, beginning with the Professional plan, which includes SDXL-Lightning and Stable Diffusion 1. Upgrading to the Creator plan will give you access to all Pro Stable Diffusion models and unlimited use of the Flux.1 model, which is the same core model used for Grok2 images.
I personally have a Professional account, so I haven't had a chance to try out Flux.1, but I have used Stable Diffusion extensively for creating character art for #NostrHeroes characters, such as these:




Nothing too spectacular when compared with some of the newer models out there, and there is no image-to-image support (yet), but more than adequate for casual image generation needs. Moreover, it is far more than what one would expect from a simple media-hosting service.
Admittedly, I am also no expert at coaxing AI models to produce anything remarkable so your results may vary. Either way, image generation is a welcome tool to have available without needing to go to an outside service unless you require something very specific.
Upload Limits
The maximum file size limits on Nostr.Build have been getting progressively larger, even for their free service. As I recall, it was a mere 21MB limit per file just a few months ago, which is fine for image files, but is quickly exceeded with videos. Then they increased their limits to 50MB per file, and as of recent updates it has been increased once more to a whopping 100MB per file... for free! This is more than adequate for most uses.
However, free users' images, GIFs, and videos are automatically viewable via Nostr.Build's free media gallery. This is something to particularly bear in mind when uploading images you intend to share via direct message. Though your DMs are encrypted, the images uploaded to Nostr.Build are not, and if you don't have a paid account, they will be viewable to the all paid users in the free media gallery. If you want to upload images that will not be viewable unless you actively share them, you must have a paid account.
Paid accounts have no file size limit, but they do have a total storage limit. I could not find anything about total storage limits for free accounts, but Professional tier will give you 25GB, Creator 50GB, and Advanced 250GB. Uploads to paid accounts are not visible in the free media gallery, so only those you give the link to will be able to access your content.
Media Types
Many file types are supported by Nostr.Built, even for free users, including:
- Image: .jpg, .png, .gif
- Video: .mov, mp4
- Audio: mp3, .wav
Upgrading to the Professional plan will add .pdf and .svg to the list of permitted file types, and upgrading to Creator or above will add .zip files, as well.
I believe other common file types are also supported, but these are the only ones specifically mentioned on the site.
Free Media Gallery
The free media gallery is an interesting little feature that Nostr.Build has available to paid accounts. Free users can get a preview, such as the one below, but only paid users can browse through the millions of uploads made by free users.
Apart from being amusing to browse through the things people have been uploading, I am unsure of how useful this particular feature is. No indication is given as to who uploaded the media, and it is limited compared to media feeds in other Nostr apps in two important ways. First, it only shows media uploaded to Nostr.Build, while other media-focused Nostr apps, such as Slidestr, Lumina, or even Primal will show media posted by all Nostr users. Second, Nostr.Build's gallery doesn't show all uploads to Nostr.Build, but only uploads from those without a paid account, further limiting the scope of whose uploads are seen.
Paid users have the advantage of being able to upload media that is not viewable to anyone unless they intentionally share the link somewhere. Free users, on the other hand, must be aware that their uploads are viewable by any paid users, whether they shared the link anywhere or not.
One incident I had while testing out another app required me to reach out to Nostr.Build support to request deletion of an image. It had some of my personal information in it, and had been uploaded to Nostr.Build and sent to me via DM. The sender assumed that since it was being sent via DM, no one else would be able to see the image, but because he was not a paid user of Nostr.Build, the image was included in the Free Media Gallery for any paid user to see. Not ideal, but the folks at Nostr.Build were quick to get it deleted for me.
In short, I have mixed feelings about this particular feature.
Blossom
Blossom is a media storage and retrieval protocol built for Nostr, but usable with any application that needs to access media via the web, and Nostr.Build has recently added support for Blossom uploads via their Blossom server: blossom.band
I will likely be adding a Nostrversity article going over Blossom in detail in the near future, but here's the basics of what it makes possible:
First, easy integration for media uploading from your favorite Nostr apps. Amethyst, Coracle, Primal and others have added Blossom upload support, so you just have to hop into your settings and add Nostr.Build's Blossom server address to start using it as your media host. No need to go to a separate app to upload your media and copy/paste the URL into your Nostr note!
Second, your media in Blossom is content addressable. This means it is named based on a hash of its actual data. Because of this, you can verify that the media has not been altered or replaced by your media host. If the hash doesn't match the data, it won't be loaded by the Nostr client, so you never have to worry about the image in your note being replaced by a different image by your media host.
Finally, because your media is addressable by its content, you can save the same media to multiple hosts, and if one of them goes down, Nostr apps can fetch your media from other hosts, just like they can do with your notes by fetching them from different relays if one relay you write to is down. This makes your images and videos much harder to censor, since you would need to be banned by multiple Blossom servers for your media to no longer be accessible.
If you would like to upload media to more than one Blossom server at the same time, your options are currently to use Primal and ensure that your settings have "Enable media mirrors" toggled on, or to use Bouquet. Hopefully we will see this option added to more Nostr apps in the near future.
Metadata Stripping
For files uploaded via Nostr.Build's dashboard, location metadata is removed upon upload. This is to protect user privacy, since this data could be used to reveal your home address if it is left attached to images posted publicly on Nostr.
When uploading via Blossom, media containing location metadata will be rejected. The user will be required to remove the metadata before they can upload the media.
No KYC and No Ads Policy
The only form of identification needed to use Nostr.Build is your Nostr identity. Every upload is tied to your npub, but no name, date of birth, email, or other identifying information is required. This is made possible because Nostr.Build only accepts Bitcoin as payment for their accounts, and no KYC is required to make Bitcoin transactions via Lightning.
Additionally, Nostr.Build is philosophically opposed to targeted advertising, so they have a policy that they will never use ads on their hosting service.
Client Integrations
Even before Blossom, Nostr.Build had many Nostr clients that used it as the default media hosting service, allowing users to upload directly within the app. This has only expanded now that Nostr.Build has added Blossom.
A very non-exhaustive list of clients that integrate with Nostr.Build is listed on their site, and includes Damus, Amethyst, Nostrudel, Snort, Iris, Coracle, Flycat, and Yakihonne. Additional apps that support Nostr.Build via Blossom include Primal and Flotilla. Some of these integrations support both Blossom and NIP-96 options for uploading media, such as Amethyst, while others only support one or the other.
I would not be surprised to see more and more Nostr apps move to integrating Blossom and phasing out NIP-96 support. Either way, though, Nostr.Build currently supports both, and is therefore an excellent hosting option if you want to use it with a wide range of Nostr apps.
Media Statistics
For those with a paid account, Nostr.Build provides information about how often each of your uploads has been requested and viewed within a given time period.
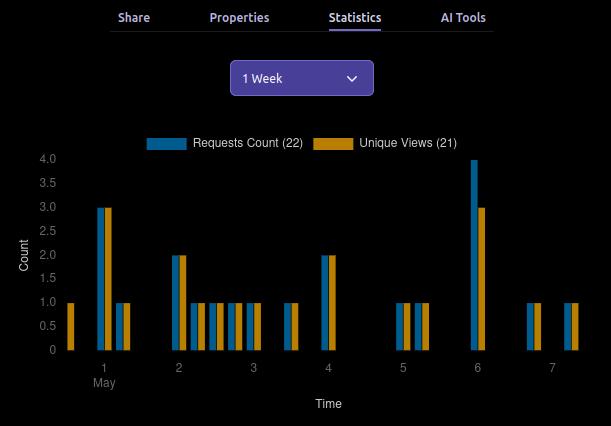
This can be valuable information for content creators, so they can determine what content is resonating with their audience, and what times of day their posts get the most views.
This information can currently be viewed for a maximum period of three months prior to the current date, and as short a period as just the past hour.
Can My Grandma Use It?
Score: 4.7 / 5
Nostr.Build is incredibly easy to use if you have a paid account, or if you are a free user uploading to Nostr.Build through a client that integrates with them by default. Previous frictions encountered by free users trying to upload large files should now be few and far between, thanks to the generous 100MB size limit.
Where things may be a bit more involved is when users are trying to set up media hosting on Nostr apps that don't use Nostr.Build by default. Exactly where in the settings the user must go to set this up, and whether to use the Blossom or NIP-96 address may not be immediately apparent, and requires an understanding of the difference that the user may not possess. This is not the fault of Nostr.Built, though, and I have not taken it into consideration in the scoring. Each individual Nostr app's settings should be as easy to understand as possible.
Another point of friction may come from free users who want to upload directly through the Nostr.Build site, instead of via another Nostr app. This used to be possible without logging in, but in an effort to ensure the service was used for Nostr, and not for general media hosting, Nostr.Build added the requirement to log in.
Thankfully, there are plenty of login options, including npub and password, browser extension (NIP-07), and even via a one-time-code sent to you via Nostr DM. However, if you don't have a paid account already, logging in will prompt you to upgrade. It seems that uploading directly via the website has been removed for free users entirely. You can only upload via another Nostr app if you don't have a paid account. This may lead to confusion for users who don't want to pay for an account, since it isn't made apparent anywhere that uploading through the website isn't an option for them.
Additionally, I would like to see the addresses for the Blossom server and for NIP-96 uploads (unless they are being phased out) added to the main page somewhere. Even selecting the "Blossom" page from the site navigation doesn't make clear what needs to be done to utilize the service. Something as simple as, "To use Nostr.Build with your favorite Blossom compatible Nostr apps, just add https://blossom.band as your media host in the app settings," would be enough to point users in the right direction.
For those who do have paid accounts, the dashboard is easy to navigate and organize your media.
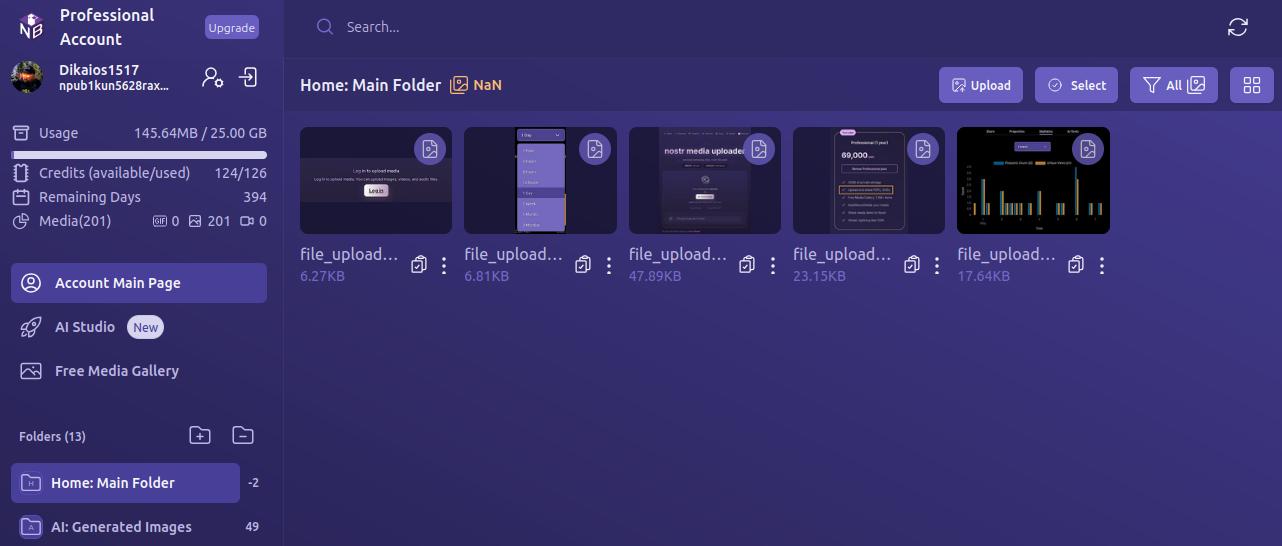
By default, all uploads are added to the Main Folder. Users can leave them there, or they can easily create new folders and drag and drop media to organize it.
Every image has a copy/paste clipboard icon for ready access to copy the media URL for inclusion into a Nostr note.
Additionally, Nostr.Build allows users to share their uploaded media to Nostr directly from the dashboard. Bear in mind, though, this is published to a set of popular relays, without taking into account the user's preferred write relays.
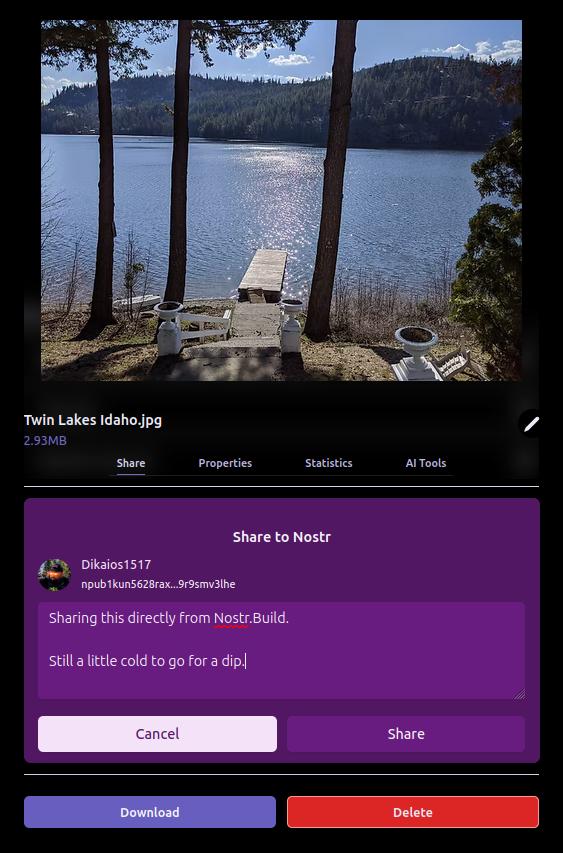
The section just below the user's profile information gives an at-a-glance view of important information, such as how much of the user's allotted storage has been used, how many AI Studio credits are available, how many days are left before their paid account must be renewed, and how many files from three major categories — GIFs, images, and videos — have been uploaded.

Uploading directly to the dashboard is also incredibly easy. You can simply drag and drop files into the upload pane, or browse for them. If you have a URL for the media you want to upload, you can even paste it to import from another website or Blossom server.
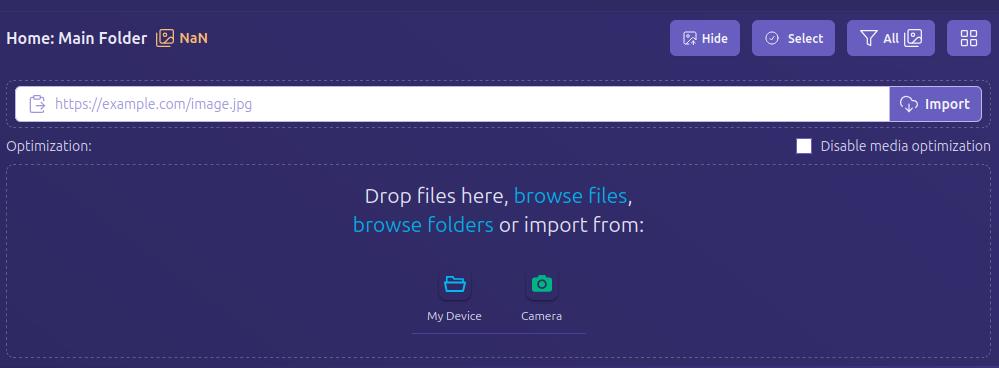
Anything I could think of that I might want to do in the interface was intuitive to find, well labeled, or had common and easily identified icons.
How do UI look?
Score: 4.7 / 5
I would describe Nostr.Build's UI as clean and utilitarian, which is what one would expect from a media hosting service. Nothing too flashy. Just what you need and nothing you don't.
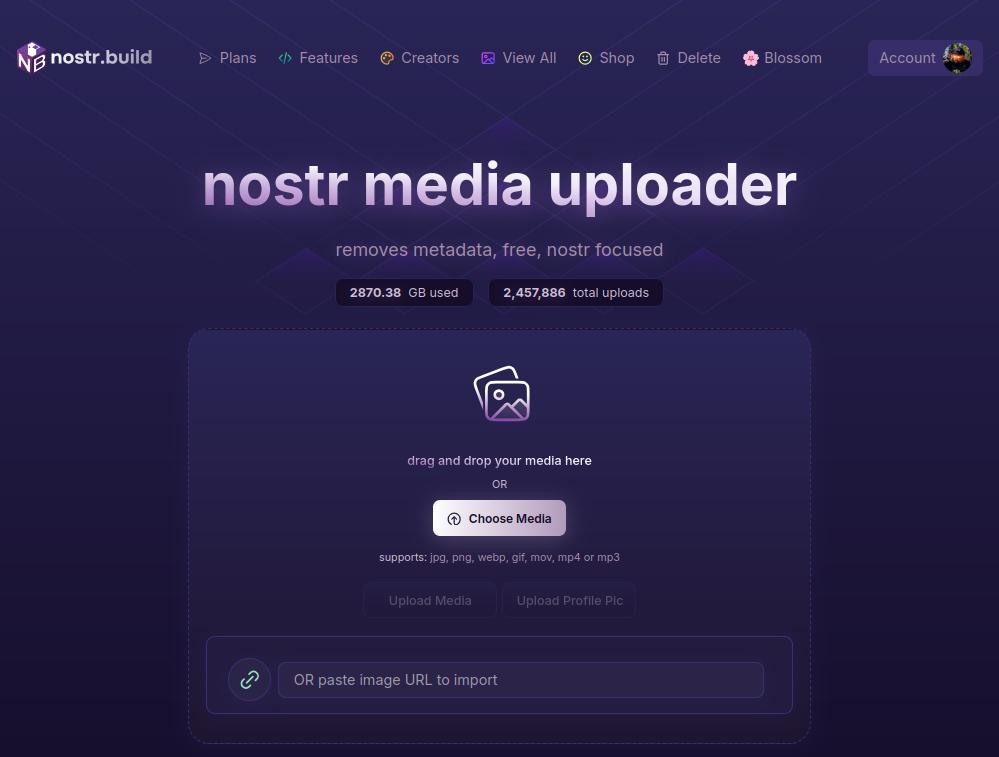
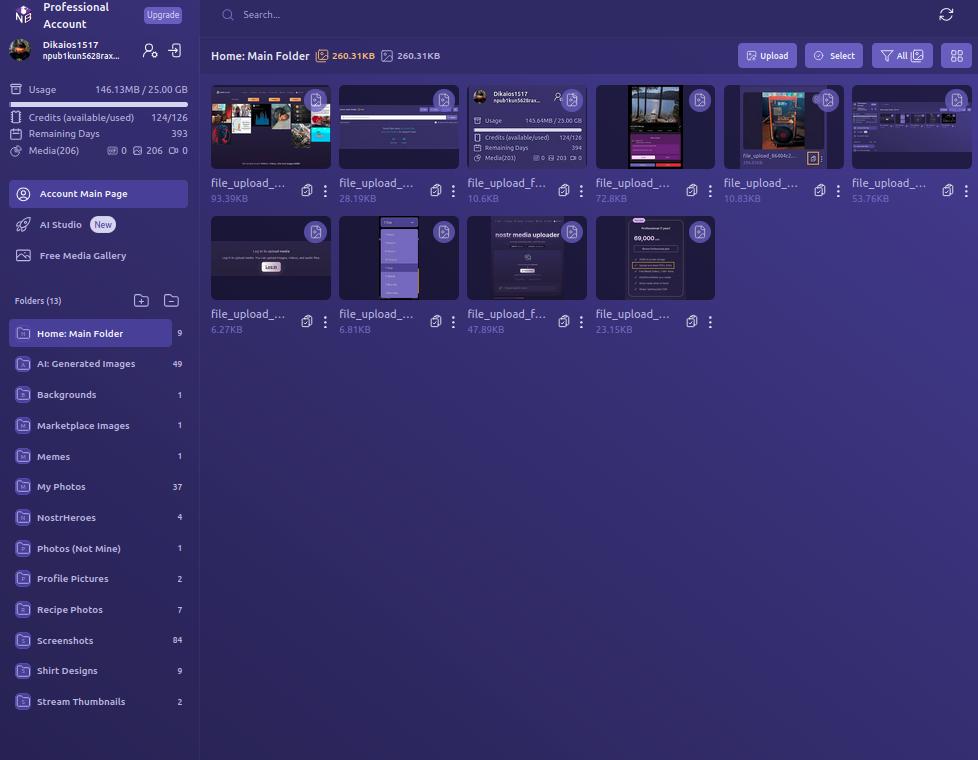
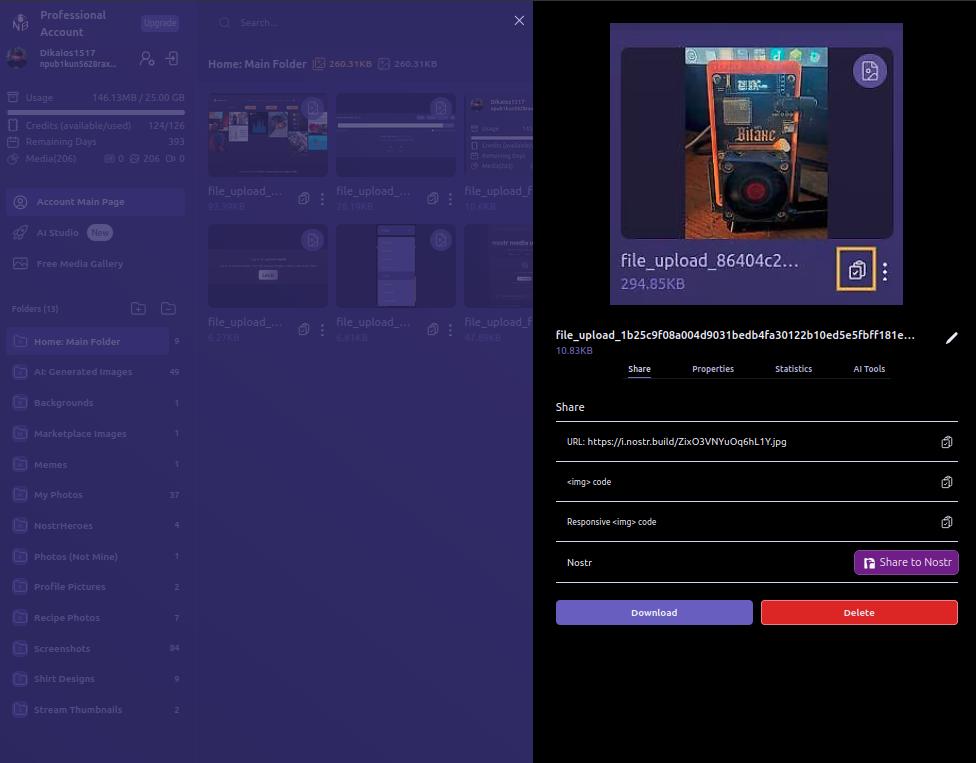
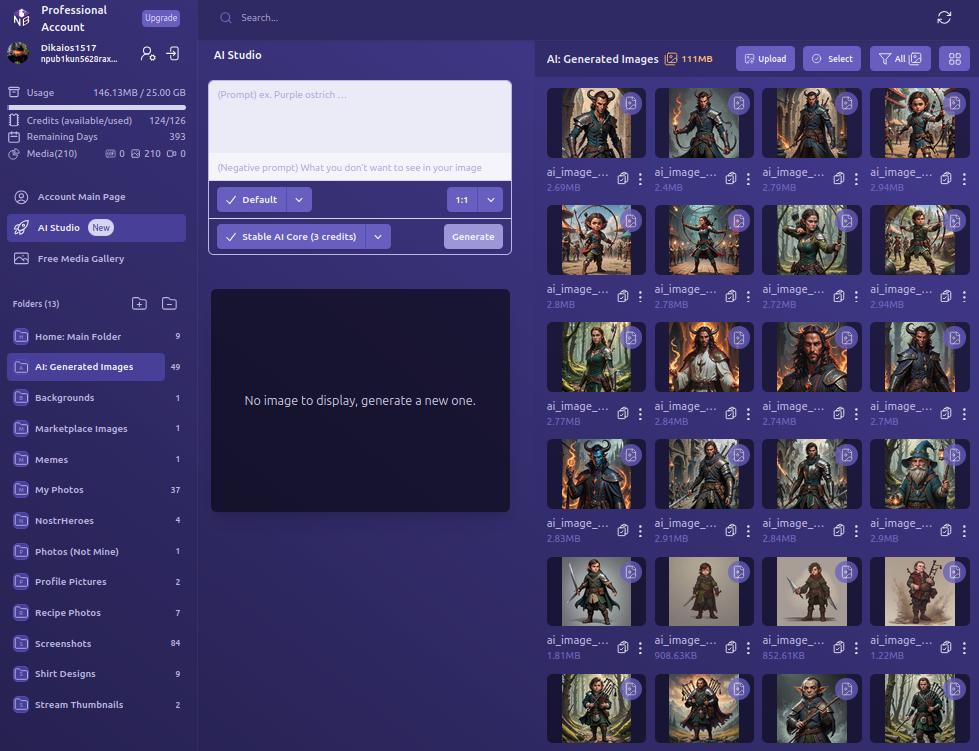
We certainly like our purple color-schemes on Nostr, and Nostr.Build leans into that with white text on shades of purple backgrounds, along with occasional color-popping accents. If a Nostr client had made the same color choices, I might be a bit more critical, but it works in an app that users won't be spending a ton of time in, except while managing their media, or using the AI Studio to generate some images.
UI elements such as buttons, active folder indicators, and icons all maintain an attractive, and simple design, with rounded corners wherever appropriate. Nothing looks too busy or overbearing, and the spacing between image previews in the folder view is just right.
Font remains consistent throughout the interface, with no jarring changes, and bold text, in white or another contrasting color, is used appropriately to draw attention, while subdued text is rendered in a light purple to blend more with the background, while remaining readable.
As such, the UI is attractive, without being particularly breathtaking. Nothing to complain about, but also nothing to write home about.
Log In Options
Score: 4.8 / 5
As mentioned previously, Nostr.Build provides three ways a user can log in.
The first should be very familiar for any Nostr user who frequents web clients, and that is by use of a browser extension (NIP-07), such as Alby, Nos2x, or Gooti. Note, this will also work if you are on Android and using KeyChat's browser, which has a NIP-07 signer built in.
Next is the legacy login method for Nostr.Build that they have used since the service first launched, which is via npub and password. This should serve to remind you that even though Nostr.Build supports Nostr login, and can post your images to Nostr for you, it's really just a centralized media hosting service. Just like you wouldn't use only one Nostr relay, you should not use just one media host. Mirror your media to other Blossom servers.
Most intriguing, and one I had not seen used before, is the option to use your npub and have a one-time-code sent to you via Nostr DM. I tested this method out and it worked flawlessly. It is unfortunately using the old NIP-04 DM spec, though, so any clients that have deprecated these DMs will not work for receiving the code. We're in a strange place with Nostr DMs currently, with some clients deprecating NIP-04 DMs in favor of NIP-17, others that still only support NIP-04, and a few that support both. If you don't see the DM in your client of choice, hop over to Primal and check your DMs there in the "other" tab.
Since Nostr.Build is supporting Nostr login, I would like to see them add remote signer (NIP-46) login alongside browser extension login to round out the options expected from a Nostr web app.
Feature Set
Score: 4.8 / 5
The features provided by Nostr.Build all work as expected and provide a lot of value to the user. With only one exception, all of the features make sense for a media hosting and management service to provide, and they are adding more features all the time.
Users not only get a reliable hosting service, with excellent uptime for their media, but they get integrations with most Nostr clients I can think of, Blossom protocol support, media organization and statistics, posting media to Nostr from within the dashboard, metadata stripping for enhanced privacy, a wide range of supported file types, and an AI image generation studio! What's more, there are additional features already on the roadmap, including traditional and AI image editing, additional plan options, expandable storage, and video transcoding for optimized playback. Nostr.Build is just getting started and they already offer more than most media hosting services out there, intended for Nostr or otherwise.
The one feature I am still not sold on is the "Free Media Gallery." The name is misleading. The gallery itself is not free. You must have a paid account to access more than a preview of it. Rather, it displays media uploaded by free users, regardless of whether they uploaded that media to send via DM, or uploaded it but decided not to share it out, or uploaded it to post it only within a private group on Flotilla, or uploaded it and only sent the note with the image link to a private relay.
Moreover, if I want to see media that has been shared on Nostr, there are plenty of ways I can do so that I can be confident only include media users intended to be publicly viewable. This feature from Nostr.Build, if it is kept at all, should have some way of ensuring the gallery only includes images that were shared on public relays.
Pricing
Score: 5 / 5
The pricing structure for Nostr.Build is exceptionally reasonable when compared with other services.
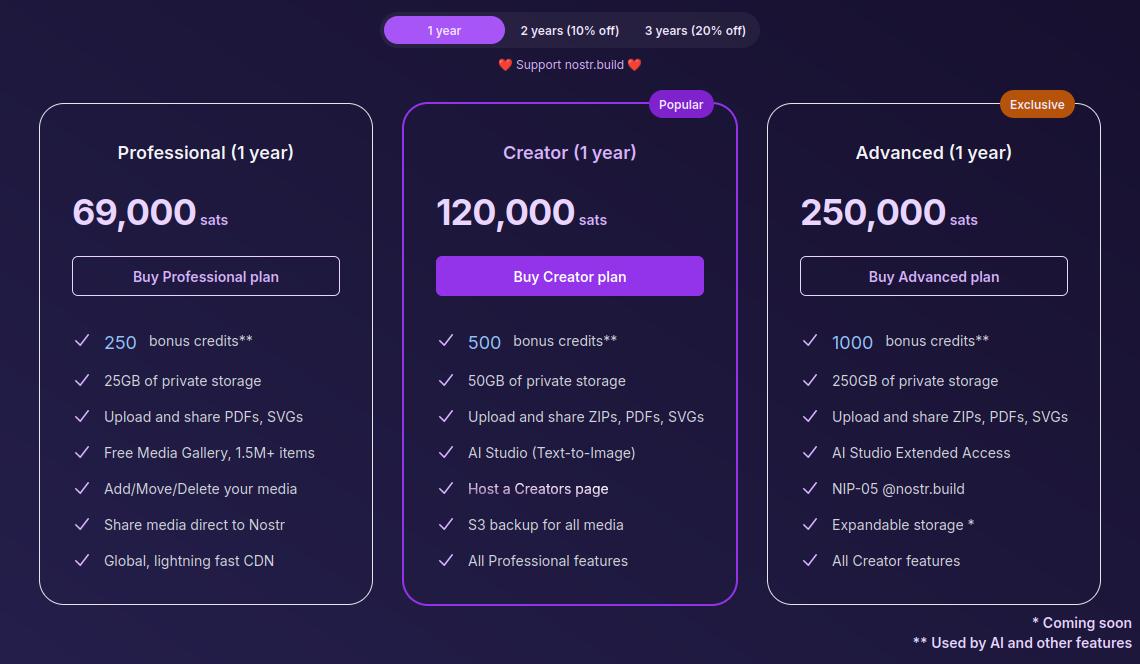
The Professional plan, which is their lowest paid tier, is just 69,000 sats a year. At current price, that translates to around $70 for the year, and Nostr.Build has been known to lower their pricing as Bitcoin goes up. Users can also get a 10% or 20% discount if they buy 2 or 3 years at a time, compensating for the fact that Bitcoin tends to go up year over year.
For that cost, users get 25GB of storage, unlimited file size for uploads within that storage cap, and access to all of Nostr.Build's features mentioned in this review, with the exception of their highest end AI models and storage of certain file types.
If I were to set up my own VPS to host a Blossom server with comparable storage, I would be paying around $14 a month before the cost of the domain, and it would be anything but plug and play. Even then, all I would have is storage. I would be missing out on all of the other features Nostr.Build has out of the box for less than half the price.
The Creator plan is close to double the cost at 120,000 sats, or about $120, a year. However, you aren't just getting double the storage space at 50GB; you are also getting double the AI credits, access to the higher tier AI models, S3 backup for all of your media, and your own Creator page you can share out with your media available for others to browse in one location.
The Advanced plan doesn't add a lot of extra features for more than double the price of the Creator plan, but it MASSIVELY increases your storage limit by 5x to a total of 250GB. Comparable storage space on a VPS to run your own Blossom server would be about $100 a month and Nostr.Build is offering it for about $250 (250,000 sats) for a whole year! If you really need to host that much media, it's hard to beat this price. The plan also comes with a Nostr.Build NIP-05 address, if you need one.
Now, the argument can be made, "But it's priced in sats, and that means in four years I will have spent many times that dollar amount on their service, possibly making it more expensive than other services priced in fiat." While that is true, it also doesn't take opportunity cost into account. Every dollar you spend on something other than Bitcoin is a missed opportunity to have bought Bitcoin with it. There's not really any difference between spending $70 in fiat to buy a hosting plan vs spending 69,000 sats, because you could have used that same $70 to buy Bitcoin instead, so you are losing out on that increase in purchasing power either way.
Not to mention, you can just buy the sats with your fiat and send it to Nostr.Build, so you would effectively be buying your plan with fiat, and they would be receiving sats.
I think Satellite.earth is still technically less expensive at just $0.05 per GB per month, which comes to $15 a year for the same 25GB of Nostr.Build's professional plan. However, all you get is media hosting. You miss out on all of the other features provided by Nostr.Build. And if you are uploading files of 100MB or less... Well, free with Nostr.Build is still cheaper than $0.5 per GB.
Wrap Up
All of the above comes together to make Nostr.Build a versatile and full-featured media hosting and management service at an affordable price point for their paid accounts, but with no need to pay at all if you just want a place to upload photos, GIFs, memes, and even some videos, so long as the file size stays under 100MB. Whether you want to use Nostr.Build as your primary media host, or as just one redundancy in your Blossom set up, they have you covered and I encourage you to check them out!
For the next review, I would like to go with another client, this time for the web, and the two options I am debating between are Coracle.social and Jumble.social. Let me know in the comments which you would like to see!
-
 @ eb0157af:77ab6c55
2025-05-28 14:01:59
@ eb0157af:77ab6c55
2025-05-28 14:01:59Banking giants JPMorgan, Bank of America, Citigroup, and Wells Fargo are in talks to develop a unified stablecoin solution.
According to the Wall Street Journal on May 22, some of the largest financial institutions in the United States are exploring the possibility of joining forces to launch a stablecoin.
Subsidiaries of JPMorgan, Bank of America, Citigroup, and Wells Fargo have initiated preliminary discussions for a joint stablecoin issuance, according to sources close to the matter cited by the WSJ. Also at the negotiating table are Early Warning Services, the parent company of the digital payments network Zelle, and the payment network Clearing House.
The talks are reportedly still in the early stages, and any final decision could change depending on regulatory developments and market demand for stablecoins.
Stablecoin regulation
On May 20, the US Senate voted 66 to 32 to advance discussion of the Guiding and Establishing National Innovation for US Stablecoins Act (GENIUS Act), a specific law to regulate stablecoins. The bill outlines a regulatory framework for stablecoin collateralization and mandates compliance with anti-money laundering rules.
David Sacks, White House crypto advisor, expressed optimism about the bill’s bipartisan approval. However, senior Democratic Party officials intend to amend the bill to include a clause preventing former President Donald Trump and other US officials from profiting from stablecoins.
Demand for stablecoins has increased, with total market capitalization rising to $245 billion from $205 billion at the beginning of the year, a 20% increase.
The post Major US banks consider launching a joint stablecoin appeared first on Atlas21.
-
 @ 0d97beae:c5274a14
2025-01-11 16:52:08
@ 0d97beae:c5274a14
2025-01-11 16:52:08This article hopes to complement the article by Lyn Alden on YouTube: https://www.youtube.com/watch?v=jk_HWmmwiAs
The reason why we have broken money
Before the invention of key technologies such as the printing press and electronic communications, even such as those as early as morse code transmitters, gold had won the competition for best medium of money around the world.
In fact, it was not just gold by itself that became money, rulers and world leaders developed coins in order to help the economy grow. Gold nuggets were not as easy to transact with as coins with specific imprints and denominated sizes.
However, these modern technologies created massive efficiencies that allowed us to communicate and perform services more efficiently and much faster, yet the medium of money could not benefit from these advancements. Gold was heavy, slow and expensive to move globally, even though requesting and performing services globally did not have this limitation anymore.
Banks took initiative and created derivatives of gold: paper and electronic money; these new currencies allowed the economy to continue to grow and evolve, but it was not without its dark side. Today, no currency is denominated in gold at all, money is backed by nothing and its inherent value, the paper it is printed on, is worthless too.
Banks and governments eventually transitioned from a money derivative to a system of debt that could be co-opted and controlled for political and personal reasons. Our money today is broken and is the cause of more expensive, poorer quality goods in the economy, a larger and ever growing wealth gap, and many of the follow-on problems that have come with it.
Bitcoin overcomes the "transfer of hard money" problem
Just like gold coins were created by man, Bitcoin too is a technology created by man. Bitcoin, however is a much more profound invention, possibly more of a discovery than an invention in fact. Bitcoin has proven to be unbreakable, incorruptible and has upheld its ability to keep its units scarce, inalienable and counterfeit proof through the nature of its own design.
Since Bitcoin is a digital technology, it can be transferred across international borders almost as quickly as information itself. It therefore severely reduces the need for a derivative to be used to represent money to facilitate digital trade. This means that as the currency we use today continues to fare poorly for many people, bitcoin will continue to stand out as hard money, that just so happens to work as well, functionally, along side it.
Bitcoin will also always be available to anyone who wishes to earn it directly; even China is unable to restrict its citizens from accessing it. The dollar has traditionally become the currency for people who discover that their local currency is unsustainable. Even when the dollar has become illegal to use, it is simply used privately and unofficially. However, because bitcoin does not require you to trade it at a bank in order to use it across borders and across the web, Bitcoin will continue to be a viable escape hatch until we one day hit some critical mass where the world has simply adopted Bitcoin globally and everyone else must adopt it to survive.
Bitcoin has not yet proven that it can support the world at scale. However it can only be tested through real adoption, and just as gold coins were developed to help gold scale, tools will be developed to help overcome problems as they arise; ideally without the need for another derivative, but if necessary, hopefully with one that is more neutral and less corruptible than the derivatives used to represent gold.
Bitcoin blurs the line between commodity and technology
Bitcoin is a technology, it is a tool that requires human involvement to function, however it surprisingly does not allow for any concentration of power. Anyone can help to facilitate Bitcoin's operations, but no one can take control of its behaviour, its reach, or its prioritisation, as it operates autonomously based on a pre-determined, neutral set of rules.
At the same time, its built-in incentive mechanism ensures that people do not have to operate bitcoin out of the good of their heart. Even though the system cannot be co-opted holistically, It will not stop operating while there are people motivated to trade their time and resources to keep it running and earn from others' transaction fees. Although it requires humans to operate it, it remains both neutral and sustainable.
Never before have we developed or discovered a technology that could not be co-opted and used by one person or faction against another. Due to this nature, Bitcoin's units are often described as a commodity; they cannot be usurped or virtually cloned, and they cannot be affected by political biases.
The dangers of derivatives
A derivative is something created, designed or developed to represent another thing in order to solve a particular complication or problem. For example, paper and electronic money was once a derivative of gold.
In the case of Bitcoin, if you cannot link your units of bitcoin to an "address" that you personally hold a cryptographically secure key to, then you very likely have a derivative of bitcoin, not bitcoin itself. If you buy bitcoin on an online exchange and do not withdraw the bitcoin to a wallet that you control, then you legally own an electronic derivative of bitcoin.
Bitcoin is a new technology. It will have a learning curve and it will take time for humanity to learn how to comprehend, authenticate and take control of bitcoin collectively. Having said that, many people all over the world are already using and relying on Bitcoin natively. For many, it will require for people to find the need or a desire for a neutral money like bitcoin, and to have been burned by derivatives of it, before they start to understand the difference between the two. Eventually, it will become an essential part of what we regard as common sense.
Learn for yourself
If you wish to learn more about how to handle bitcoin and avoid derivatives, you can start by searching online for tutorials about "Bitcoin self custody".
There are many options available, some more practical for you, and some more practical for others. Don't spend too much time trying to find the perfect solution; practice and learn. You may make mistakes along the way, so be careful not to experiment with large amounts of your bitcoin as you explore new ideas and technologies along the way. This is similar to learning anything, like riding a bicycle; you are sure to fall a few times, scuff the frame, so don't buy a high performance racing bike while you're still learning to balance.
-
 @ 37fe9853:bcd1b039
2025-01-11 15:04:40
@ 37fe9853:bcd1b039
2025-01-11 15:04:40yoyoaa
-
 @ 812cff5a:5c40aeeb
2025-05-28 12:56:32
@ 812cff5a:5c40aeeb
2025-05-28 12:56:32NIP-01 — الشكل الأساسي للأحداث في نُستر
رقم التعريف (NIP): 01
العنوان: الشكل الأساسي للأحداث
الحالة: نهائي
المؤلف: fiatjaf
التاريخ: 2020-12-10
الملخص
هذا المستند يعرّف الشكل القياسي لأي "حدث" يتم تداوله ضمن شبكة نُستر (Nostr).
الهدف من هذا التنسيق هو ضمان إمكانية معالجة وتفسير الأحداث من قبل جميع العملاء والخوادم بطريقة موحّدة.
هيكل الحدث
كل حدث عبارة عن كائن يحتوي على الحقول التالية:
{ "id": <معرّف فريد>, "pubkey": <مفتاح عام للمرسل>, "created_at": <تاريخ الإنشاء كرقم UNIX timestamp>, "kind": <نوع الحدث>, "tags": [<قائمة من الوسوم>], "content": <المحتوى>, "sig": <التوقيع الرقمي> }
شرح الحقول
- id: سلسلة نصية تمثل SHA-256 لمحتوى الحدث.
- pubkey: المفتاح العام للمستخدم (عادةً 32 بايت بصيغة hex).
- created_at: الطابع الزمني للإنشاء (Unix timestamp).
- kind: رقم يحدد نوع الحدث (مثلاً: منشور، متابعة، إعادة نشر).
- tags: قائمة من الوسوم المرتبطة بالحدث (مثلاً: إشارة إلى مستخدم أو حدث).
- content: المحتوى الأساسي للحدث (نص أو بيانات).
- sig: التوقيع الرقمي الذي يثبت أن المرسل هو صاحب المحتوى.
كيفية توليد معرف الحدث
idيتم توليد المعرّف عبر أخذ تمثيل JSON للحدث (بدون الحقول
idوsig) ثم حساب التجزئة باستخدام SHA-256.
توقيع الحدث
يُوقّع المستخدم الحدث باستخدام مفتاحه الخاص.
هذا التوقيع الرقمي يسمح لأي شخص بالتحقق من صحة الحدث باستخدام المفتاح العام.
أنواع الأحداث (kind)
0: ملف التعريف (الاسم، الصورة، النبذة).1: منشور عام نصي.2: إعادة نشر.3: قائمة المتابَعين.4: رسالة مشفّرة خاصة.- أنواع أخرى يمكن إضافتها لاحقًا.
الوسوم (Tags)
الوسوم عبارة عن قوائم (arrays) داخل الحدث لتوفير معلومات إضافية.
مثال:["e", "<معرّف الحدث>"] ["p", "<مفتاح عام لمستخدم>"]"e"تشير إلى حدث."p"تشير إلى مستخدم.
الخلاصة
NIP-01 هو الأساس الهيكلي لتبادل الأحداث عبر نُستر.
من خلال اتباع هذا الشكل، يمكن لجميع التطبيقات والخوادم العمل معاً بسلاسة، وضمان أمن وموثوقية كل حدث. -
 @ 5f078e90:b2bacaa3
2025-05-28 12:00:23
@ 5f078e90:b2bacaa3
2025-05-28 12:00:23Sylvi the seahorse

In the coral haven of Azure Bay, a seahorse named Sylvi danced with the tides. Her tail curled around a swaying frond as she watched fish dart by. One dawn, a lost pearl rolled into her nook. Sylvi, curious, nudged it along the reef, meeting crabs and eels who shared tales of the deep. By dusk, she found its oyster home. The pearl gleamed thanks, and Sylvi twirled home, her heart light as foam.
Ignore this test. This was in bold originally.
(380 chars, plain text after Markdown stripping, this was in italics originally)
Originally written on habla.news (on Nostr)
-
 @ 06830f6c:34da40c5
2025-05-24 04:21:03
@ 06830f6c:34da40c5
2025-05-24 04:21:03The evolution of development environments is incredibly rich and complex and reflects a continuous drive towards greater efficiency, consistency, isolation, and collaboration. It's a story of abstracting away complexity and standardizing workflows.
Phase 1: The Bare Metal & Manual Era (Early 1970s - Late 1990s)
-
Direct OS Interaction / Bare Metal Development:
- Description: Developers worked directly on the operating system's command line or a basic text editor. Installation of compilers, interpreters, and libraries was a manual, often arcane process involving downloading archives, compiling from source, and setting environment variables. "Configuration drift" (differences between developer machines) was the norm.
- Tools: Text editors (Vi, Emacs), command-line compilers (GCC), Makefiles.
- Challenges: Extremely high setup time, dependency hell, "works on my machine" syndrome, difficult onboarding for new developers, lack of reproducibility. Version control was primitive (e.g., RCS, SCCS).
-
Integrated Development Environments (IDEs) - Initial Emergence:
- Description: Early IDEs (like Turbo Pascal, Microsoft Visual Basic) began to integrate editors, compilers, debuggers, and sometimes GUI builders into a single application. This was a massive leap in developer convenience.
- Tools: Turbo Pascal, Visual Basic, early Visual Studio versions.
- Advancement: Improved developer productivity, streamlined common tasks. Still relied on local system dependencies.
Phase 2: Towards Dependency Management & Local Reproducibility (Late 1990s - Mid-2000s)
-
Basic Build Tools & Dependency Resolvers (Pre-Package Managers):
- Description: As projects grew, manual dependency tracking became impossible. Tools like Ant (Java) and early versions of
autoconf/makefor C/C++ helped automate the compilation and linking process, managing some dependencies. - Tools: Apache Ant, GNU Autotools.
- Advancement: Automated build processes, rudimentary dependency linking. Still not comprehensive environment management.
- Description: As projects grew, manual dependency tracking became impossible. Tools like Ant (Java) and early versions of
-
Language-Specific Package Managers:
- Description: A significant leap was the emergence of language-specific package managers that could fetch, install, and manage libraries and frameworks declared in a project's manifest file. Examples include Maven (Java), npm (Node.js), pip (Python), RubyGems (Ruby), Composer (PHP).
- Tools: Maven, npm, pip, RubyGems, Composer.
- Advancement: Dramatically simplified dependency resolution, improved intra-project reproducibility.
- Limitation: Managed language-level dependencies, but not system-level dependencies or the underlying OS environment. Conflicts between projects on the same machine (e.g., Project A needs Python 2.7, Project B needs Python 3.9) were common.
Phase 3: Environment Isolation & Portability (Mid-2000s - Early 2010s)
-
Virtual Machines (VMs) for Development:
- Description: To address the "it works on my machine" problem stemming from OS-level and system-level differences, developers started using VMs. Tools like VMware Workstation, VirtualBox, and later Vagrant (which automated VM provisioning) allowed developers to encapsulate an entire OS and its dependencies for a project.
- Tools: VMware, VirtualBox, Vagrant.
- Advancement: Achieved strong isolation and environment reproducibility (a true "single environment" for a project).
- Limitations: Resource-heavy (each VM consumed significant CPU, RAM, disk space), slow to provision and boot, difficult to share large VM images.
-
Early Automation & Provisioning Tools:
- Description: Alongside VMs, configuration management tools started being used to automate environment setup within VMs or on servers. This helped define environments as code, making them more consistent.
- Tools: Chef, Puppet, Ansible.
- Advancement: Automated provisioning, leading to more consistent environments, often used in conjunction with VMs.
Phase 4: The Container Revolution & Orchestration (Early 2010s - Present)
-
Containerization (Docker):
- Description: Docker popularized Linux Containers (LXC), offering a lightweight, portable, and efficient alternative to VMs. Containers package an application and all its dependencies into a self-contained unit that shares the host OS kernel. This drastically reduced resource overhead and startup times compared to VMs.
- Tools: Docker.
- Advancement: Unprecedented consistency from development to production (Dev/Prod Parity), rapid provisioning, highly efficient resource use. Became the de-facto standard for packaging applications.
-
Container Orchestration:
- Description: As microservices and container adoption grew, managing hundreds or thousands of containers became a new challenge. Orchestration platforms automated the deployment, scaling, healing, and networking of containers across clusters of machines.
- Tools: Kubernetes, Docker Swarm, Apache Mesos.
- Advancement: Enabled scalable, resilient, and complex distributed systems development and deployment. The "environment" started encompassing the entire cluster.
Phase 5: Cloud-Native, Serverless & Intelligent Environments (Present - Future)
-
Cloud-Native Development:
- Description: Leveraging cloud services (managed databases, message queues, serverless functions) directly within the development workflow. Developers focus on application logic, offloading infrastructure management to cloud providers. Containers become a key deployment unit in this paradigm.
- Tools: AWS Lambda, Azure Functions, Google Cloud Run, cloud-managed databases.
- Advancement: Reduced operational overhead, increased focus on business logic, highly scalable deployments.
-
Remote Development & Cloud-Based IDEs:
- Description: The full development environment (editor, terminal, debugger, code) can now reside in the cloud, accessed via a thin client or web browser. This means developers can work from any device, anywhere, with powerful cloud resources backing their environment.
- Tools: GitHub Codespaces, Gitpod, AWS Cloud9, VS Code Remote Development.
- Advancement: Instant onboarding, consistent remote environments, access to high-spec machines regardless of local hardware, enhanced security.
-
Declarative & AI-Assisted Environments (The Near Future):
- Description: Development environments will become even more declarative, where developers specify what they need, and AI/automation tools provision and maintain it. AI will proactively identify dependency issues, optimize resource usage, suggest code snippets, and perform automated testing within the environment.
- Tools: Next-gen dev container specifications, AI agents integrated into IDEs and CI/CD pipelines.
- Prediction: Near-zero environment setup time, self-healing environments, proactive problem identification, truly seamless collaboration.
web3 #computing #cloud #devstr
-
-
 @ 62033ff8:e4471203
2025-01-11 15:00:24
@ 62033ff8:e4471203
2025-01-11 15:00:24收录的内容中 kind=1的部分,实话说 质量不高。 所以我增加了kind=30023 长文的article,但是更新的太少,多个relays 的服务器也没有多少长文。
所有搜索nostr如果需要产生价值,需要有高质量的文章和新闻。 而且现在有很多机器人的文章充满着浪费空间的作用,其他作用都用不上。
https://www.duozhutuan.com 目前放的是给搜索引擎提供搜索的原材料。没有做UI给人类浏览。所以看上去是粗糙的。 我并没有打算去做一个发microblog的 web客户端,那类的客户端太多了。
我觉得nostr社区需要解决的还是应用。如果仅仅是microblog 感觉有点够呛
幸运的是npub.pro 建站这样的,我觉得有点意思。
yakihonne 智能widget 也有意思
我做的TaskQ5 我自己在用了。分布式的任务系统,也挺好的。
-
 @ 23b0e2f8:d8af76fc
2025-01-08 18:17:52
@ 23b0e2f8:d8af76fc
2025-01-08 18:17:52Necessário
- Um Android que você não use mais (a câmera deve estar funcionando).
- Um cartão microSD (opcional, usado apenas uma vez).
- Um dispositivo para acompanhar seus fundos (provavelmente você já tem um).
Algumas coisas que você precisa saber
- O dispositivo servirá como um assinador. Qualquer movimentação só será efetuada após ser assinada por ele.
- O cartão microSD será usado para transferir o APK do Electrum e garantir que o aparelho não terá contato com outras fontes de dados externas após sua formatação. Contudo, é possível usar um cabo USB para o mesmo propósito.
- A ideia é deixar sua chave privada em um dispositivo offline, que ficará desligado em 99% do tempo. Você poderá acompanhar seus fundos em outro dispositivo conectado à internet, como seu celular ou computador pessoal.
O tutorial será dividido em dois módulos:
- Módulo 1 - Criando uma carteira fria/assinador.
- Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
No final, teremos:
- Uma carteira fria que também servirá como assinador.
- Um dispositivo para acompanhar os fundos da carteira.

Módulo 1 - Criando uma carteira fria/assinador
-
Baixe o APK do Electrum na aba de downloads em https://electrum.org/. Fique à vontade para verificar as assinaturas do software, garantindo sua autenticidade.
-
Formate o cartão microSD e coloque o APK do Electrum nele. Caso não tenha um cartão microSD, pule este passo.

- Retire os chips e acessórios do aparelho que será usado como assinador, formate-o e aguarde a inicialização.

- Durante a inicialização, pule a etapa de conexão ao Wi-Fi e rejeite todas as solicitações de conexão. Após isso, você pode desinstalar aplicativos desnecessários, pois precisará apenas do Electrum. Certifique-se de que Wi-Fi, Bluetooth e dados móveis estejam desligados. Você também pode ativar o modo avião.\ (Curiosidade: algumas pessoas optam por abrir o aparelho e danificar a antena do Wi-Fi/Bluetooth, impossibilitando essas funcionalidades.)

- Insira o cartão microSD com o APK do Electrum no dispositivo e instale-o. Será necessário permitir instalações de fontes não oficiais.

- No Electrum, crie uma carteira padrão e gere suas palavras-chave (seed). Anote-as em um local seguro. Caso algo aconteça com seu assinador, essas palavras permitirão o acesso aos seus fundos novamente. (Aqui entra seu método pessoal de backup.)

Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
-
Criar uma carteira somente leitura em outro dispositivo, como seu celular ou computador pessoal, é uma etapa bastante simples. Para este tutorial, usaremos outro smartphone Android com Electrum. Instale o Electrum a partir da aba de downloads em https://electrum.org/ ou da própria Play Store. (ATENÇÃO: O Electrum não existe oficialmente para iPhone. Desconfie se encontrar algum.)
-
Após instalar o Electrum, crie uma carteira padrão, mas desta vez escolha a opção Usar uma chave mestra.

- Agora, no assinador que criamos no primeiro módulo, exporte sua chave pública: vá em Carteira > Detalhes da carteira > Compartilhar chave mestra pública.

-
Escaneie o QR gerado da chave pública com o dispositivo de consulta. Assim, ele poderá acompanhar seus fundos, mas sem permissão para movimentá-los.
-
Para receber fundos, envie Bitcoin para um dos endereços gerados pela sua carteira: Carteira > Addresses/Coins.
-
Para movimentar fundos, crie uma transação no dispositivo de consulta. Como ele não possui a chave privada, será necessário assiná-la com o dispositivo assinador.

- No assinador, escaneie a transação não assinada, confirme os detalhes, assine e compartilhe. Será gerado outro QR, desta vez com a transação já assinada.

- No dispositivo de consulta, escaneie o QR da transação assinada e transmita-a para a rede.
Conclusão
Pontos positivos do setup:
- Simplicidade: Basta um dispositivo Android antigo.
- Flexibilidade: Funciona como uma ótima carteira fria, ideal para holders.
Pontos negativos do setup:
- Padronização: Não utiliza seeds no padrão BIP-39, você sempre precisará usar o electrum.
- Interface: A aparência do Electrum pode parecer antiquada para alguns usuários.
Nesse ponto, temos uma carteira fria que também serve para assinar transações. O fluxo de assinar uma transação se torna: Gerar uma transação não assinada > Escanear o QR da transação não assinada > Conferir e assinar essa transação com o assinador > Gerar QR da transação assinada > Escanear a transação assinada com qualquer outro dispositivo que possa transmiti-la para a rede.
Como alguns devem saber, uma transação assinada de Bitcoin é praticamente impossível de ser fraudada. Em um cenário catastrófico, você pode mesmo que sem internet, repassar essa transação assinada para alguém que tenha acesso à rede por qualquer meio de comunicação. Mesmo que não queiramos que isso aconteça um dia, esse setup acaba por tornar essa prática possível.
-
 @ 866e0139:6a9334e5
2025-05-27 10:15:17
@ 866e0139:6a9334e5
2025-05-27 10:15:17Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Der Schweizer Historiker Daniele Ganser startet eine Plakataktion. Auf Facebook schreibt er:
"Dieses Plakat habe ich ab heute an sechs Bahnhöfen in der Schweiz aufhängen lassen: Die Schweiz muss die Neutralität bewahren. Keine Zusammenarbeit mit der NATO!
Die Aktion läuft eine Woche. Das Plakat hängt in Basel (Gleis 5 und 7), Zürich (Gleis 9 und 12), Bern (Gleis 3 und 11), Luzern (Gleis 7 und 11), St. Gallen (Gleis 1 und 2) und Chur (Gleis 4 und Arosabahn).
Wenn jemand ein Plakat sieht und fotografiert und es mir per Email schickt freut mich das!
https://globalbridge.ch/die-schweiz-muss-die.../
Daniele Ganser kann man über folgende Seite kontaktieren.
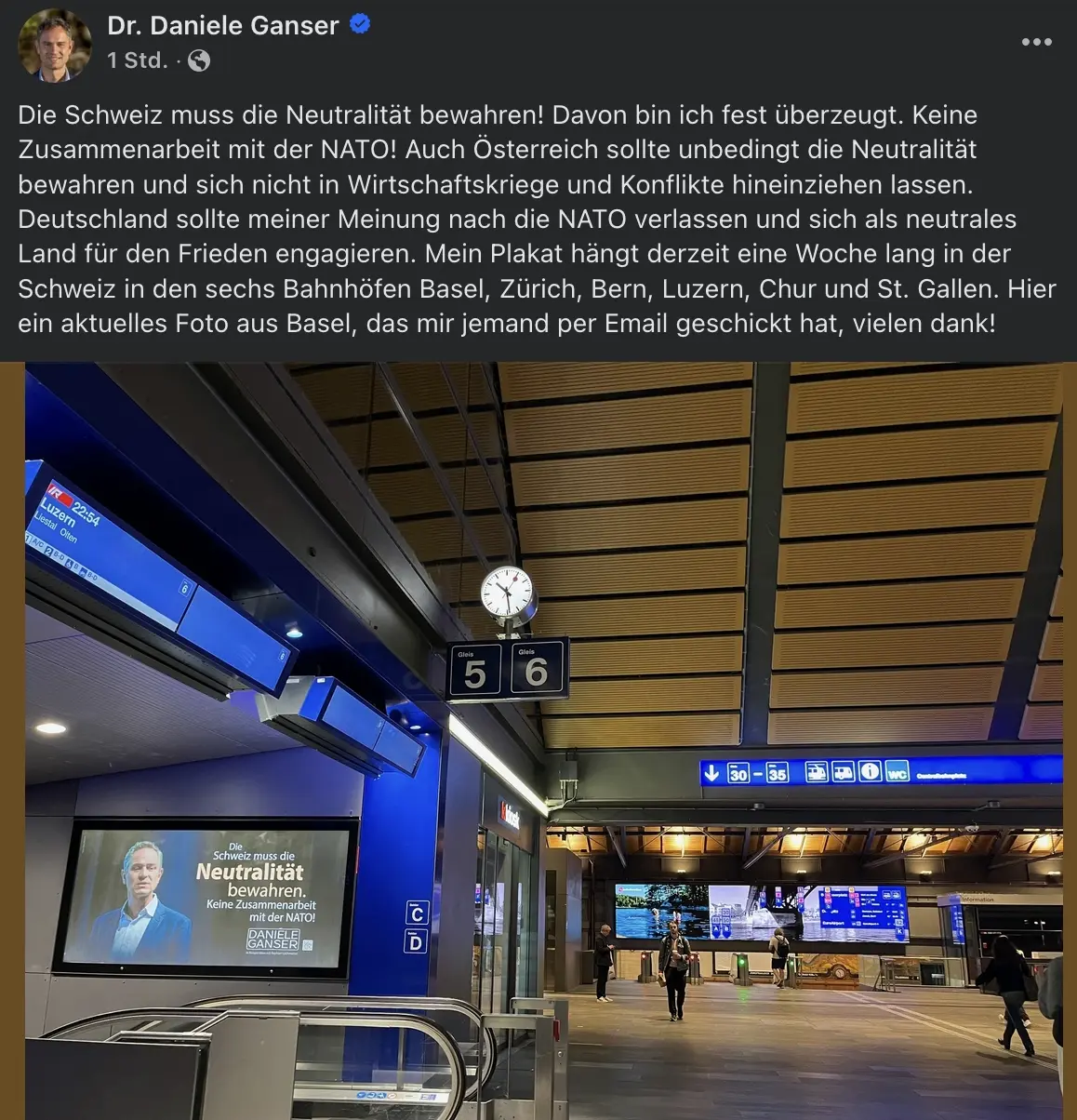
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 005bc4de:ef11e1a2
2025-05-28 09:05:10
@ 005bc4de:ef11e1a2
2025-05-28 09:05:10
BIP-2,100,000,000,000,000,000
So, you're telling me...
- 21 million bitcoins is out, and...
- 2.1 quadrillion sats is in, except that...
- sats are out, so...
- 2.1 quadrillion bitcoins is in, except that...
- there are actually millisats, but...
- millisats are out, so...
- millibitcoins are in, so now...
- there are 2.1 quintillion millibitcoins, except that...
- millibitcoins are the basic base unit of bitcoin, so...
- millibitcoins are out, and now...
- 2.1 quintillion bitcoins are in
-
 @ eb0157af:77ab6c55
2025-05-28 13:01:38
@ eb0157af:77ab6c55
2025-05-28 13:01:38A fake Uber driver steals $73,000 in XRP and $50,000 in Bitcoin after drugging an American tourist.
A U.S. citizen vacationing in the United Kingdom fell victim to a scam that cost him $123,000 in cryptocurrencies stored on his smartphone. The man was drugged by an individual posing as an Uber driver.
According to My London, Jacob Irwin-Cline had spent the evening at a London nightclub, consuming several alcoholic drinks before requesting an Uber ride home. The victim admitted he hadn’t carefully verified the booking details on his device, mistakenly getting into a private taxi driven by someone who, at first glance, resembled the expected Uber driver but was using a completely different vehicle.
Once inside the car, the American tourist reported that the driver offered him a cigarette, allegedly laced with scopolamine — a rare and powerful sedative. Irwin-Cline described how the smoke made him extremely docile and fatigued, causing him to lose consciousness for around half an hour.
Upon waking, the driver ordered the victim to get out of the vehicle. As Irwin-Cline stepped out, the man suddenly accelerated, running him over and fleeing with his mobile phone, which contained the private keys and access to his cryptocurrencies. Screenshots provided to MyLondon show that $73,000 worth of XRP and $50,000 in bitcoin had been transferred to various wallets.
This incident adds to a growing trend of kidnappings, extortions, armed robberies, and ransom attempts targeting crypto executives, investors, and their families.
Just a few weeks ago, the daughter and grandson of Pierre Noizat, CEO of crypto exchange Paymium, were targeted in a kidnapping attempt in Paris. The incident took place in broad daylight when attackers tried to force the family into a parked vehicle. However, Noizat’s daughter managed to fight off the assailants.
The post American tourist drugged and robbed: $123,000 in crypto stolen in London appeared first on Atlas21.
-
 @ 207ad2a0:e7cca7b0
2025-01-07 03:46:04
@ 207ad2a0:e7cca7b0
2025-01-07 03:46:04Quick context: I wanted to check out Nostr's longform posts and this blog post seemed like a good one to try and mirror. It's originally from my free to read/share attempt to write a novel, but this post here is completely standalone - just describing how I used AI image generation to make a small piece of the work.
Hold on, put your pitchforks down - outside of using Grammerly & Emacs for grammatical corrections - not a single character was generated or modified by computers; a non-insignificant portion of my first draft originating on pen & paper. No AI is ~~weird and crazy~~ imaginative enough to write like I do. The only successful AI contribution you'll find is a single image, the map, which I heavily edited. This post will go over how I generated and modified an image using AI, which I believe brought some value to the work, and cover a few quick thoughts about AI towards the end.
Let's be clear, I can't draw, but I wanted a map which I believed would improve the story I was working on. After getting abysmal results by prompting AI with text only I decided to use "Diffuse the Rest," a Stable Diffusion tool that allows you to provide a reference image + description to fine tune what you're looking for. I gave it this Microsoft Paint looking drawing:
and after a number of outputs, selected this one to work on:
The image is way better than the one I provided, but had I used it as is, I still feel it would have decreased the quality of my work instead of increasing it. After firing up Gimp I cropped out the top and bottom, expanded the ocean and separated the landmasses, then copied the top right corner of the large landmass to replace the bottom left that got cut off. Now we've got something that looks like concept art: not horrible, and gets the basic idea across, but it's still due for a lot more detail.

The next thing I did was add some texture to make it look more map like. I duplicated the layer in Gimp and applied the "Cartoon" filter to both for some texture. The top layer had a much lower effect strength to give it a more textured look, while the lower layer had a higher effect strength that looked a lot like mountains or other terrain features. Creating a layer mask allowed me to brush over spots to display the lower layer in certain areas, giving it some much needed features.
At this point I'd made it to where I felt it may improve the work instead of detracting from it - at least after labels and borders were added, but the colors seemed artificial and out of place. Luckily, however, this is when PhotoFunia could step in and apply a sketch effect to the image.
At this point I was pretty happy with how it was looking, it was close to what I envisioned and looked very visually appealing while still being a good way to portray information. All that was left was to make the white background transparent, add some minor details, and add the labels and borders. Below is the exact image I wound up using:

Overall, I'm very satisfied with how it turned out, and if you're working on a creative project, I'd recommend attempting something like this. It's not a central part of the work, but it improved the chapter a fair bit, and was doable despite lacking the talent and not intending to allocate a budget to my making of a free to read and share story.
The AI Generated Elephant in the Room
If you've read my non-fiction writing before, you'll know that I think AI will find its place around the skill floor as opposed to the skill ceiling. As you saw with my input, I have absolutely zero drawing talent, but with some elbow grease and an existing creative direction before and after generating an image I was able to get something well above what I could have otherwise accomplished. Outside of the lowest common denominators like stock photos for the sole purpose of a link preview being eye catching, however, I doubt AI will be wholesale replacing most creative works anytime soon. I can assure you that I tried numerous times to describe the map without providing a reference image, and if I used one of those outputs (or even just the unedited output after providing the reference image) it would have decreased the quality of my work instead of improving it.
I'm going to go out on a limb and expect that AI image, text, and video is all going to find its place in slop & generic content (such as AI generated slop replacing article spinners and stock photos respectively) and otherwise be used in a supporting role for various creative endeavors. For people working on projects like I'm working on (e.g. intended budget $0) it's helpful to have an AI capable of doing legwork - enabling projects to exist or be improved in ways they otherwise wouldn't have. I'm also guessing it'll find its way into more professional settings for grunt work - think a picture frame or fake TV show that would exist in the background of an animated project - likely a detail most people probably wouldn't notice, but that would save the creators time and money and/or allow them to focus more on the essential aspects of said work. Beyond that, as I've predicted before: I expect plenty of emails will be generated from a short list of bullet points, only to be summarized by the recipient's AI back into bullet points.
I will also make a prediction counter to what seems mainstream: AI is about to peak for a while. The start of AI image generation was with Google's DeepDream in 2015 - image recognition software that could be run in reverse to "recognize" patterns where there were none, effectively generating an image from digital noise or an unrelated image. While I'm not an expert by any means, I don't think we're too far off from that a decade later, just using very fine tuned tools that develop more coherent images. I guess that we're close to maxing out how efficiently we're able to generate images and video in that manner, and the hard caps on how much creative direction we can have when using AI - as well as the limits to how long we can keep it coherent (e.g. long videos or a chronologically consistent set of images) - will prevent AI from progressing too far beyond what it is currently unless/until another breakthrough occurs.
-
 @ 75869cfa:76819987
2025-04-28 14:51:12
@ 75869cfa:76819987
2025-04-28 14:51:12GM, Nostriches!
The Nostr Review is a biweekly newsletter focused on Nostr statistics, protocol updates, exciting programs, the long-form content ecosystem, and key events happening in the Nostr-verse. If you’re interested, join me in covering updates from the Nostr ecosystem!
Quick review:
In the past two weeks, Nostr statistics indicate over 216,000 daily trusted pubkey events. The number of new users has seen a notable decrease, Profiles with contact lists and pubkeys writing events were both representing a 70% decline. More than 7 million events have been published, reflecting a 24% decrease. Total Zap activity stands at approximately 16 million, marking a 20% increase.
Additionally, 14 pull requests were submitted to the Nostr protocol, with 6 merged. A total of 45 Nostr projects were tracked, with 7 releasing product updates, and over 378 long-form articles were published, 24% focusing on Bitcoin and Nostr. During this period, 9 notable events took place, and 3 significant events are upcoming.
Nostr Statistics
Based on user activity, the total daily trusted pubkeys writing events is about 216,000, representing a slight 2 % decrease compared to the previous period. Daily activity peaked at 17483 events, with a low of approximately 15499.
The number of new users has decreased significantly.Profiles with contact lists and pubkeys writing events were 26,132 and 59,403 respectively, both representing a decline of approximately 70% compared to the previous period.
The total number of note events published is around 7 million, reflecting a 24% decrease.Posts remain the most dominant category by volume, totaling approximately 1.7 million, representing a 4% decrease compared to the previous period.Reposts, however, saw a significant increase, rising by 33% compared to the same period.
For zap activity, the total zap amount is about 16 million, showing an decrease of over 20% compared to the previous period.
Data source: https://stats.nostr.band/
NIPs
Allow multi-user AUTH #1881 vitorpamplona is proposing a PR that reuses one connection for everyone by accepting multi-user logins on the relay side. Additionally, this PR standardizes how relays should handle multiple AUTH messages from the client, instead of leaving it as undefined behavior. Currently, most relays override the previous AUTH, which means developers can rotate the authenticated user within the same connection. Some relays only accept the first AUTH and ignore the rest. A few newer relays already support multi-user logins as described in this PR, which he believes is the correct way to implement NIP-42 AUTH. The purpose of this PR is to formalize that behavior.
Adds optional nip60.signSecret() and kind 10019 filter tag #1890 robwoodgate is proposing a PR that clarifies and improves Nostr <---> Cashu interoperability as follows:Adds an optional signer signature for NUT-10 well-known secrets to NIP-60, NIP-07 and NIP-46;Clarifies use of Nostr <---> Cashu public keys in NIP-61;Adds an optional reverse lookup filter tag to NIP-61 kind 10019 events.
Notable Projects
Coracle 0.6.10 nostr:npub13myx4j0pp9uenpjjq68wdvqzywuwxfj64welu28mdvaku222mjtqzqv3qk
Coracle 0.6.10 release is out on the web and zapstore! This is another maintenance release, including a complete rewrite of the networking code (coming soon to flotilla), and several bug fixes. * Fix spotify url parsing bug * Fix nip46 signer connect * Use new version of network library * Fix reply drafts bug * Fix creating a new account while logged in * Re-work storage adapter to minimize storage and improve performance * Improve initial page load times * Fix followers page * Upgrade welshman * Remove platform relay * Show PoW * Don't fetch messages until decryption is enabled
Damus v1.14 nostr:npub18m76awca3y37hkvuneavuw6pjj4525fw90necxmadrvjg0sdy6qsngq955
A new TestFlight release is here for Purple users to try! * ️Setup a wallet lightning fast with our new one-click wallet setup, powered by Coinos! * New revamped wallet experience with balance and transactions view for your NWC wallet — see how much you got zapped without even leaving the app! * New notification setting to hide hellthreads. ie. Achieve notification peace. * NIP-65 relay list support — more compatibility across Nostr apps! * Unicode 16 emoji reactions (only for iOS 18.4+) - even more options to express your reactions! * Blurred images now show some more information — no more wondering why images are occasionally blurred. * More bugs fixed, and general robustness improvements.
0xchat v1.4.9 nostr:npub1tm99pgz2lth724jeld6gzz6zv48zy6xp4n9xu5uqrwvx9km54qaqkkxn72
What's new: * Implemented updated NIP-29 group logic with support for group admin roles * Added support for Aegis URL scheme login on iOS
YakiHonne nostr:npub1yzvxlwp7wawed5vgefwfmugvumtp8c8t0etk3g8sky4n0ndvyxesnxrf8q
🌐web v4.6.0: * Introducing Smart Widgets v2 – now dynamic and programmable. Learn more at https://yakihonne.com/docs/sw/intro * New Tools Smart Widgets section in note creation for advanced content editing. * Curations, videos, and polls are now Tools Smart Widgets, enabling quick creation and seamless embedding in notes. * Zap advertisements added—top zappers can now appear below notes. * Note translation button has been relocated next to the note options for easier access. * Followers and following lists are now visible directly on the dashboard home page. * General improvements and bug fixes for a smoother experience.
📱mobile v1.7.0: * Introducing the fully upgraded smart widget with its expanded set of functionalities. * A set of tools to enhance content editing. * Curations, videos, and polls are now Tools Smart Widgets, enabling quick creation and seamless embedding in notes. * Shortened URLs for a better user experience. * Highest zappers in notes will be highlighted. * Zapper list now includes zaps messages. * Videos and curations are no longer visible in the app. * Gossip models can be enabled and disabled. * Fixed multiple bugs for a more stable and seamless app experience. * Enhanced overall performance, usability, and design across the app.
Nostur v1.20 nostr:npub1n0stur7q092gyverzc2wfc00e8egkrdnnqq3alhv7p072u89m5es5mk6h0
New in this version: * Added support for Lists (kind 30000) * Show preview of feed from list * Turn list into feed tab with 1 tap * Subscribe toggle to keep updating the feed from original maintainer, or keep list as-is * Share List: Toggle to make list public * Lists tab on Profile view * 'Add all contacts to feed/list' post menu item * Discover tab now shows Lists shared by your follows * Enable manual ordering of custom feeds / tabs * New Top Zapped feed * New onboarding screens * New default color scheme / adjusted backgrounds * Lower delays and timeouts for fetching things * Improved hellthread handling * Support for comment on highlights (kind 9802) * Toggle to post to restricted/locked relay when starting post from single relay feed * Support relay auth for bunker/remote signer accounts * Zoom for previous profile pictures * Improved Relay Autopilot / Outbox when loading a single profile, always try to find 2 additional relays not in already used relay set * Improved support for accounts with large follow lists * Keep things longer in cache on desktop version * Improved support for pasting animated gifs * Use floating mini video player also on iPad and Desktop * Many performance improvements and bugfixes
Zapstore 0.2.6 nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8
- Fixes for stale data, apps should now show their latest versions
- Upgrade to nostr:npub1kpt95rv4q3mcz8e4lamwtxq7men6jprf49l7asfac9lnv2gda0lqdknhmz DVM format
- New Developer screen (basic for now, delete local cache if apps are missing!)
ZEUS v0.11.0 nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5
ZEUS v0.11.0-alpha 2 with Cashu support is now available for testing. In this build: * Fix: addresses an issue where some Cashu wallets would crash when redeeming their first token. If you were affected by this bug, try removing the mint in question and re-adding it with the 'Existing funds' toggle enabled. FUNDS ARE SAFU! * Feat: Core Lightning: show closed channels list * Locale updates
Long-Form Content Eco
In the past two weeks, more than 378 long-form articles have been published, including over 57 articles on Bitcoin and more than 32 related to Nostr, accounting for 24% of the total content.
These articles about Nostr mainly explore the protocol’s steady evolution toward simplicity, decentralization, and practical usability. There is a clear call within the community to strip away unnecessary complexity and return to Nostr’s minimalist roots, emphasizing lightweight structures and user autonomy. At the same time, a wave of innovation is expanding Nostr’s possibilities—new marketplaces, interoperable bridges with other protocols, and creative tools for publishing, identity, and social interaction are emerging rapidly. The articles also reflect a growing focus on censorship resistance, advocating for more diverse and independent relay networks, encrypted communications between relays, and broader user control over data and publishing. Practical guides and firsthand user experiences reveal both the excitement and the challenges of building within an open, permissionless ecosystem.
These articles about Bitcoin depict the evolution and expansion of the Bitcoin ecosystem from various perspectives. On the technical front, they focus on the iteration of Bitcoin Core versions, innovations in secure storage methods, advancements in multisignature solutions and post-quantum cryptography, as well as the ongoing optimization of payment tools like the Lightning Network, highlighting Bitcoin's continuous progress in enhancing asset security and transaction efficiency. At the same time, through real-life stories and personal experiences, many articles illustrate Bitcoin's practical role in individuals' lives, showing how it helps people achieve financial autonomy, build resilience, and transform their lifestyles in times of turmoil. From a financial perspective, the articles delve into Bitcoin’s unique value as digital gold and an inflation hedge, and its function as a safe haven and transformative force in emerging economies and shifting trade environments.
Thank you, nostr:npub1jp3776ujdul56rfkkrv8rxxgrslqr07rz83xpmz3ndl74lg7ngys320eg2 nostr:npub1xzuej94pvqzwy0ynemeq6phct96wjpplaz9urd7y2q8ck0xxu0lqartaqn nostr:npub1qd6zcgzukmydscp3eyauf2dn6xzgfsevsetrls8zrzgs5t0e4fws7re0mj nostr:npub12q4tq25nvkp52sluql37yr5qn059qf3kpeaa26u0nmd7ag5xqwtscduvuh nostr:npub1t49ker2fyy2xc5y7qrsfxrp6g8evsxluqmaq09xt7uuhhzsurm3srw4jj5 nostr:npub1p7dep69xdstul0v066gcheg2ue9hg2u3pngn2p625auyuj57jkjscpn02q nostr:npub1l0cwgdrjrxsdpu6yhzkp7zcvk2zqxl20hz8mq84tlguf9cd7dgusrmk3ty nostr:npub1fn4afafnasdqcm7hnxtn26s2ye3v3g2h2xave7tcce6s7zkra52sh7yg99 npub1jh95xvxnqdqj5ljh3vahh7s7s0pv9mj9sfrkdnx4xgead9kmwpkq2e0fqm,npub1qn4ylq6s79tz4gwkphq8q4sltwurs6s36xsq2u8aw3qd5ggwzufsw3s3yz,npub1penlq56qnlvsr7v3wry24twn6jtyfw5vt6vce76yawrrajcafwfs0qmn5s,and others, for your work. Enriching Nostr’s long-form content ecosystem is crucial.
Nostriches Global Meet Ups
Recently, several Nostr events have been hosted in different countries. * Recently, YakiHonne collaborated with multiple communities and universities across Africa, such as nostr:npub1yp5maegtq53x536xcznk2hqzdtpgxg63hzhl2ya3u4nrtuasxaaqa52pzn nostr:npub1tk59m73xjqq7k3hz9hlwsvspu2xq7t9gg0qj86cgp4rrlqew5lpq5zq7qp nostr:npub1wjncl8k8z86qq2hwqqeufa4g9z35r5t5wquawxghnrs06z9ds8zsm49yg7 and more, to successfully host seven Nostr Workshops, attracting over 200 enthusiastic participants. The events not only provided a comprehensive introduction to the Nostr ecosystem and Bitcoin payments but also offered hands-on experiences with decentralized technologies through the YakiHonne platform.
- The second BOBSpace Nostr Month Meetup took place on Friday, April 25, 2025, at 6:30 PM in Bangkok. This special event featured nostr:npub18k67rww6547vdf74225x4p6hfm4zvhs8t8w7hp75fcrj0au7mzxs30202m the developer of Thailand’s home-grown Nostr client Wherostr, as the guest speaker. He shared his developer journey, the story behind building Wherostr, and how Nostr enables censorship-resistant communication. This was a Bitcoin-only meetup focused on the Nostr protocol and decentralized technologies.
- Panama Blockchain Week 2025 took place from April 22 to 24 at the Panama Convention Center in Panama City. As the first large-scale blockchain event in Central America, it aimed to position Panama as a leading blockchain financial hub in Latin America. The event featured a diverse lineup, including a blockchain conference, Investor’s Night, Web3 gaming experiences, tech exhibitions, and an after-party celebration.
Here is the upcoming Nostr event that you might want to check out. * Nostr & Poker Night will be held on April 30 at the Bitcoin Embassy in El Salvador. The event will feature an exciting Nostr-themed presentation by nostr:npub1dmnzphvk097ahcpecwfeml08xw8sg2cj4vux55m5xalqtzz9t78q6k3kv6 followed by a relaxed and fun poker night. Notably, 25% of the poker tournament prize will be donated to support MyfirstBitcoin’s Bitcoin education initiatives. * A free webinar on venture capital, Bitcoin, and cryptocurrencies will be held online on May 6 at 12:00 PM (ARG time). Organized in collaboration with Draper Cygnus, the event aims to introduce the fundamentals of venture capital, present the projects of ONG Bitcoin Argentina Academy, and provide attendees with the opportunity to interact with the guest speakers. * Bitcoin Unveiled: Demystifying Freedom Money will take place on May 10, 2025, at Almara Hub. The event will explore Bitcoin’s transformative potential, helping participants understand its purpose, learn how to get started, build a career in the Bitcoin space, and begin their Bitcoin savings journey. Featured speakers include nostr:npub1sn0q3zptdcm8qh8ktyhwtrnr9htwpykav8qnryhusr9mcr9ustxqe4tr2x Theophilus Isah, nostr:npub1s7xkezkzlfvya6ce6cuhzwswtxqm787pwddk2395pt9va4ulzjjszuz67p , and Megasley.
Additionally, We warmly invite event organizers who have held recent activities to reach out to us so we can work together to promote the prosperity and development of the Nostr ecosystem.
Thanks for reading! If there’s anything I missed, feel free to reach out and help improve the completeness and accuracy of my coverage.
-
 @ e6817453:b0ac3c39
2025-01-05 14:29:17
@ e6817453:b0ac3c39
2025-01-05 14:29:17The Rise of Graph RAGs and the Quest for Data Quality
As we enter a new year, it’s impossible to ignore the boom of retrieval-augmented generation (RAG) systems, particularly those leveraging graph-based approaches. The previous year saw a surge in advancements and discussions about Graph RAGs, driven by their potential to enhance large language models (LLMs), reduce hallucinations, and deliver more reliable outputs. Let’s dive into the trends, challenges, and strategies for making the most of Graph RAGs in artificial intelligence.
Booming Interest in Graph RAGs
Graph RAGs have dominated the conversation in AI circles. With new research papers and innovations emerging weekly, it’s clear that this approach is reshaping the landscape. These systems, especially those developed by tech giants like Microsoft, demonstrate how graphs can:
- Enhance LLM Outputs: By grounding responses in structured knowledge, graphs significantly reduce hallucinations.
- Support Complex Queries: Graphs excel at managing linked and connected data, making them ideal for intricate problem-solving.
Conferences on linked and connected data have increasingly focused on Graph RAGs, underscoring their central role in modern AI systems. However, the excitement around this technology has brought critical questions to the forefront: How do we ensure the quality of the graphs we’re building, and are they genuinely aligned with our needs?
Data Quality: The Foundation of Effective Graphs
A high-quality graph is the backbone of any successful RAG system. Constructing these graphs from unstructured data requires attention to detail and rigorous processes. Here’s why:
- Richness of Entities: Effective retrieval depends on graphs populated with rich, detailed entities.
- Freedom from Hallucinations: Poorly constructed graphs amplify inaccuracies rather than mitigating them.
Without robust data quality, even the most sophisticated Graph RAGs become ineffective. As a result, the focus must shift to refining the graph construction process. Improving data strategy and ensuring meticulous data preparation is essential to unlock the full potential of Graph RAGs.
Hybrid Graph RAGs and Variations
While standard Graph RAGs are already transformative, hybrid models offer additional flexibility and power. Hybrid RAGs combine structured graph data with other retrieval mechanisms, creating systems that:
- Handle diverse data sources with ease.
- Offer improved adaptability to complex queries.
Exploring these variations can open new avenues for AI systems, particularly in domains requiring structured and unstructured data processing.
Ontology: The Key to Graph Construction Quality
Ontology — defining how concepts relate within a knowledge domain — is critical for building effective graphs. While this might sound abstract, it’s a well-established field blending philosophy, engineering, and art. Ontology engineering provides the framework for:
- Defining Relationships: Clarifying how concepts connect within a domain.
- Validating Graph Structures: Ensuring constructed graphs are logically sound and align with domain-specific realities.
Traditionally, ontologists — experts in this discipline — have been integral to large enterprises and research teams. However, not every team has access to dedicated ontologists, leading to a significant challenge: How can teams without such expertise ensure the quality of their graphs?
How to Build Ontology Expertise in a Startup Team
For startups and smaller teams, developing ontology expertise may seem daunting, but it is achievable with the right approach:
- Assign a Knowledge Champion: Identify a team member with a strong analytical mindset and give them time and resources to learn ontology engineering.
- Provide Training: Invest in courses, workshops, or certifications in knowledge graph and ontology creation.
- Leverage Partnerships: Collaborate with academic institutions, domain experts, or consultants to build initial frameworks.
- Utilize Tools: Introduce ontology development tools like Protégé, OWL, or SHACL to simplify the creation and validation process.
- Iterate with Feedback: Continuously refine ontologies through collaboration with domain experts and iterative testing.
So, it is not always affordable for a startup to have a dedicated oncologist or knowledge engineer in a team, but you could involve consulters or build barefoot experts.
You could read about barefoot experts in my article :
Even startups can achieve robust and domain-specific ontology frameworks by fostering in-house expertise.
How to Find or Create Ontologies
For teams venturing into Graph RAGs, several strategies can help address the ontology gap:
-
Leverage Existing Ontologies: Many industries and domains already have open ontologies. For instance:
-
Public Knowledge Graphs: Resources like Wikipedia’s graph offer a wealth of structured knowledge.
- Industry Standards: Enterprises such as Siemens have invested in creating and sharing ontologies specific to their fields.
-
Business Framework Ontology (BFO): A valuable resource for enterprises looking to define business processes and structures.
-
Build In-House Expertise: If budgets allow, consider hiring knowledge engineers or providing team members with the resources and time to develop expertise in ontology creation.
-
Utilize LLMs for Ontology Construction: Interestingly, LLMs themselves can act as a starting point for ontology development:
-
Prompt-Based Extraction: LLMs can generate draft ontologies by leveraging their extensive training on graph data.
- Domain Expert Refinement: Combine LLM-generated structures with insights from domain experts to create tailored ontologies.
Parallel Ontology and Graph Extraction
An emerging approach involves extracting ontologies and graphs in parallel. While this can streamline the process, it presents challenges such as:
- Detecting Hallucinations: Differentiating between genuine insights and AI-generated inaccuracies.
- Ensuring Completeness: Ensuring no critical concepts are overlooked during extraction.
Teams must carefully validate outputs to ensure reliability and accuracy when employing this parallel method.
LLMs as Ontologists
While traditionally dependent on human expertise, ontology creation is increasingly supported by LLMs. These models, trained on vast amounts of data, possess inherent knowledge of many open ontologies and taxonomies. Teams can use LLMs to:
- Generate Skeleton Ontologies: Prompt LLMs with domain-specific information to draft initial ontology structures.
- Validate and Refine Ontologies: Collaborate with domain experts to refine these drafts, ensuring accuracy and relevance.
However, for validation and graph construction, formal tools such as OWL, SHACL, and RDF should be prioritized over LLMs to minimize hallucinations and ensure robust outcomes.
Final Thoughts: Unlocking the Power of Graph RAGs
The rise of Graph RAGs underscores a simple but crucial correlation: improving graph construction and data quality directly enhances retrieval systems. To truly harness this power, teams must invest in understanding ontologies, building quality graphs, and leveraging both human expertise and advanced AI tools.
As we move forward, the interplay between Graph RAGs and ontology engineering will continue to shape the future of AI. Whether through adopting existing frameworks or exploring innovative uses of LLMs, the path to success lies in a deep commitment to data quality and domain understanding.
Have you explored these technologies in your work? Share your experiences and insights — and stay tuned for more discussions on ontology extraction and its role in AI advancements. Cheers to a year of innovation!
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-28 12:37:30
@ 5d4b6c8d:8a1c1ee3
2025-05-28 12:37:30https://rumble.com/embed/v6rp3fh/?pub=4e023h
I know some of our stackers are follicly challenged, so I thought I'd pass along this video.
Have any of you tried topical onion juice for hair regrowth?
I'll eat more onion and rosemary and get more Sun, just to be safe.
https://stacker.news/items/991118
-
 @ 39cc53c9:27168656
2025-05-27 09:21:51
@ 39cc53c9:27168656
2025-05-27 09:21:51Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% ^1 – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% ^1 of less-than-careful criminals.
KYC? Not you.
KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. ^2
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
Your identity has been stolen
KYC data has been found to be for sale on many dark net markets^3. Exchanges may have leaks or hacks, and such leaks contain very sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. ^3
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
(they) Know Your Coins
You may already know that Bitcoin and most cryptocurrencies have a transparent public blockchain, meaning that all data is shown unencrypted for everyone to see and recorded forever. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
Conclusions
To sum up, KYC does not protect individuals; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
Edited 20/03/2024 * Add reference to the 1% statement on Rights for Illusions section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity ^1
-
 @ 58537364:705b4b85
2025-05-28 08:25:55
@ 58537364:705b4b85
2025-05-28 08:25:55ถ้าอยากแล้วไม่หลง มันก็อยากด้วยปัญญา ความอยากอย่างนี้ท่านเรียกว่า เป็นบารมีของตน แต่ไม่ใช่ทุกคนนะที่มีปัญญา
บางคนไม่อยากจะให้มันอยาก เพราะเข้าใจว่า การมาปฏิบัติก็เพื่อระงับความอยาก ความจริงน่ะ ถ้าหากว่าไม่มีความอยาก ก็ไม่มีข้อปฏิบัติ ไม่รู้ว่าจะทำอะไร ลองพิจารณาดูก็ได้
ทุกคน แม้องค์พระพุทธเจ้าของเราก็ตาม ที่ท่านออกมาปฏิบัติ ก็เพื่อจะให้บรรเทากิเลสทั้งหลายนั้น
แต่ว่ามันต้องอยากทำ อยากปฏิบัติ อยากให้มันสงบ และก็ไม่อยากให้มันวุ่นวาย ทั้งสองอย่างนี้ มันเป็นอุปสรรคทั้งนั้น ถ้าเราไม่มีปัญญา ไม่มีความฉลาดในการกระทำอย่างนั้น เพราะว่ามันปนกันอยู่ อยากทั้งสองอย่างนี้มันมีราคาเท่า ๆ กัน
อยากจะพ้นทุกข์มันเป็นกิเลส สำหรับคนไม่มีปัญญา อยากด้วยความโง่ ไม่อยากมันก็เป็นกิเลส เพราะไม่อยากอันนั้นมันประกอบด้วยความโง่เหมือนกัน คือทั้งอยาก ไม่อยาก ปัญญาก็ไม่มี ทั้งสองอย่างนี้ มันเป็นกามสุขัลลิกานุโยโค กับอัตตกิลมถานุโยโค ซึ่งพระพุทธองค์ของเรา ขณะที่พระองค์กำลังทรงปฏิบัติอยู่นั้น ท่านก็หลงใหลในอย่างนี้ ไม่รู้ว่าจะทำอย่างไร ท่านหาอุบายหลายประการ กว่าจะพบของสองสิ่งนี้
ทุกวันนี้เราทั้งหลายก็เหมือนกัน ทุกสิ่งทั้งสองอย่างนี้มันกวนอยู่ เราจึงเข้าสู่ทางไม่ได้ก็เพราะอันนี้ ความเป็นจริงนี้ทุกคนที่มาปฏิบัติ ก็เป็นปุถุชนมาทั้งนั้น ปุถุชนก็เต็มไปด้วยความอยาก ความอยากที่ไม่มีปัญญา อยากด้วยความหลง ไม่อยากมันก็มีโทษเหมือนกัน “ไม่อยาก” มันก็เป็นตัณหา “อยาก” มันก็เป็นตัณหาอีกเหมือนกัน
ทีนี้ นักปฏิบัติยังไม่รู้เรื่องว่า จะเอายังไงกัน เดินไปข้างหน้าก็ไม่ถูก เดินกลับไปข้างหลังก็ไม่ถูก จะหยุดก็หยุดไม่ได้เพราะมันยังอยากอยู่ มันยังหลงอยู่ มีแต่ความอยาก แต่ปัญญาไม่มี มันอยากด้วยความหลง มันก็เป็นตัณหา ถึงแม้ไม่อยาก มันก็เป็นความหลง มันก็เป็นตัณหาเหมือนกันเพราะอะไร? เพราะมันขาดปัญญา
ความเป็นจริงนั้น ธรรมะมันอยู่ตรงนั้นแหละ ตรงความอยากกับความไม่อยากนั่นแหละ แต่เราไม่มีปัญญา ก็พยายามไม่ให้อยากบ้าง เดี๋ยวก็อยากบ้าง อยากให้เป็นอย่างนั้น ไม่อยากให้เป็นอย่างนี้ ความจริงทั้งสองอย่างนี้ หรือทั้งคู่นี้มันตัวเดียวกันทั้งนั้น ไม่ใช่คนละตัว แต่เราไม่รู้เรื่องของมัน
พระพุทธเจ้าของเรา และสาวกทั้งหลายของพระองค์นั้นท่านก็อยากเหมือนกัน แต่ “อยาก” ของท่านนั้น เป็นเพียงอาการของจิตเฉย ๆ หรือ “ไม่อยาก” ของท่าน ก็เป็นเพียงอาการของจิตเฉย ๆ อีกเหมือนกัน มันวูบเดียวเท่านั้น ก็หายไปแล้ว
ดังนั้น ความอยากหรือไม่อยากนี้ มันมีอยู่ตลอดเวลาแต่สำหรับผู้มีปัญญานั้น “อยาก” ก็ไม่มีอุปาทาน “ไม่อยาก” ก็ไม่มีอุปาทาน เป็น “สักแต่ว่า” อยากหรือไม่อยากเท่านั้น ถ้าพูดตามความจริงแล้ว มันก็เป็นแต่ "อาการของจิต" อาการของจิตมันเป็นของมันอย่างนั้นเอง ถ้าเรามาตะครุบมันอยู่ใกล้ ๆ นี่มันก็เห็นชัด
ดังนั้นจึงว่า การพิจารณานั้น ไม่ใช่รู้ไปที่อื่น มันรู้ตรงนี้แหละ เหมือนชาวประมงที่ออกไปทอดแหนั่นแหละ ทอดแหออกไปถูกปลาตัวใหญ่ เจ้าของผู้ทอดแหจะคิดอย่างไร? ก็กลัว กลัวปลาจะออกจากแหไปเสีย เมื่อเป็นเช่นนั้น ใจมันก็ดิ้นรนขึ้นระวังมาก บังคับมาก ตะครุบไปตะครุบมาอยู่นั่นแหละ ประเดี๋ยวปลามันก็ออกจากแหไปเสีย เพราะไปตะครุบมันแรงเกินไป
อย่างนั้นโบราณท่านพูดถึงเรื่องอันนี้ ท่านว่าค่อย ๆ ทำมัน แต่อย่าไปห่างจากมัน นี่คือปฏิปทาของเรา ค่อย ๆ คลำมันไปเรื่อย ๆ อย่างนั้นแหละ
อย่าปล่อยมัน หรือไม่อยากรู้มัน ต้องรู้ ต้องรู้เรื่องของมัน พยายามทำมันไปเรื่อย ๆ ให้เป็นปฏิปทา ขี้เกียจเราก็ทำไม่ขี้เกียจเราก็ทำ เรียกว่าการทำการปฏิบัติ ต้องทำไปเรื่อยๆอย่างนี้
ถ้าหากว่าเราขยัน ขยันเพราะความเชื่อ มันมีศรัทธาแต่ปัญญาไม่มี ถ้าเป็นอย่างนี้ ขยันไป ๆ แล้วมันก็ไม่เกิดผลอะไรขึ้นมากมาย ขยันไปนาน ๆ เข้า แต่มันไม่ถูกทาง มันก็ไม่สงบระงับ ทีนี้ก็จะเกิดความคิดว่า เรานี้บุญน้อยหรือวาสนาน้อย หรือคิดไปว่ามนุษย์ในโลกนี้คงทำไม่ได้หรอก แล้วก็เลยหยุดเลิกทำเลิกปฏิบัติ
ถ้าเกิดความคิดอย่างนี้เมื่อใด ขอให้ระวังให้มาก ให้มีขันติ ความอดทน ให้ทำไปเรื่อย ๆ เหมือนกับเราจับปลาตัวใหญ่ ก็ให้ค่อย ๆ คลำมันไปเรื่อย ๆ ปลามันก็จะไม่ดิ้นแรงค่อย ๆทำไปเรื่อย ๆ ไม่หยุด ไม่ช้าปลาก็จะหมดกำลัง มันก็จับง่าย จับให้ถนัดมือเลย ถ้าเรารีบจนเกินไป ปลามันก็จะหนีดิ้นออกจากแหเท่านั้น
ดังนั้น การปฏิบัตินี้ ถ้าเราพิจารณาตามพื้นเหตุของเรา เช่นว่า เราไม่มีความรู้ในปริยัติ ไม่มีความรู้ในอะไรอื่น ที่จะให้การปฏิบัติมันเกิดผลขึ้น ก็ดูความรู้ที่เป็นพื้นเพเดิมของเรานั่นแหละอันนั้นก็คือ “ธรรมชาติของจิต” นี่เอง มันมีของมันอยู่แล้ว เราจะไปเรียนรู้มัน มันก็มีอยู่ หรือเราจะไม่ไปเรียนรู้มัน มันก็มีอยู่
อย่างที่ท่านพูดว่า พระพุทธเจ้าจะบังเกิดขึ้นก็ตาม หรือไม่บังเกิดขึ้นก็ตาม ธรรมะก็คงมีอยู่อย่างนั้น มันเป็นของมันอยู่อย่างนั้น ไม่พลิกแพลงไปไหน มันเป็นสัจจธรรม
เราไม่เข้าใจสัจจธรรม ก็ไม่รู้ว่าสัจจธรรมเป็นอย่างไร นี้เรียกว่า การพิจารณาในความรู้ของผู้ปฏิบัติที่ไม่มีพื้นปริยัติ
ขอให้ดูจิต พยายามอ่านจิตของเจ้าของ พยายามพูดกับจิตของเจ้าของ มันจึงจะรู้เรื่องของจิต ค่อย ๆ ทำไป ถ้ายังไม่ถึงที่ของมัน มันก็ไปอยู่อย่างนั้น
ครูบาอาจารย์บางท่านบอกว่า ทำไปเรื่อย ๆ อย่าหยุด บางทีเรามาคิด “เออ ทำไปเรื่อย ๆ ถ้าไม่รู้เรื่องของมัน ถ้าทำไม่ถูกที่มัน มันจะรู้อะไร” อย่างนี้เป็นต้น ก็ต้องไปเรื่อย ๆ ก่อน แล้วมันก็จะเกิดความรู้สึกนึกคิดขึ้นในสิ่งที่เราพากเพียรทำนั้น
มันเหมือนกันกับบุรุษที่ไปสีไฟ ได้ฟังท่านบอกว่า เอาไม้ไผ่สองอันมาสีกันเข้าไปเถอะ แล้วจะมีไฟเกิดขึ้น บุรุษนั้นก็จับไม้ไผ่เข้าสองอัน สีกันเข้า แต่ใจร้อน สีไปได้หน่อย ก็อยากให้มันเป็นไฟ ใจก็เร่งอยู่เรื่อย ให้เป็นไฟเร็วๆ แต่ไฟก็ไม่เกิดสักที บุรุษนั้นก็เกิดความขี้เกียจ แล้วก็หยุดพัก แล้วจึงลองสีอีกนิด แล้วก็หยุดพัก ความร้อนที่พอมีอยู่บ้าง ก็หายไปล่ะซิ เพราะความร้อนมันไม่ติดต่อกัน
ถ้าทำไปเรื่อยๆอย่างนี้ เหนื่อยก็หยุด มีแต่เหนื่อยอย่างเดียวก็พอได้ แต่มีขี้เกียจปนเข้าด้วย เลยไปกันใหญ่ แล้วบุรุษนั้นก็หาว่าไฟไม่มี ไม่เอาไฟ ก็ทิ้ง เลิก ไม่สีอีก แล้วก็ไปเที่ยวประกาศว่า ไฟไม่มี ทำอย่างนี้ไม่ได้ ไม่มีไฟหรอก เขาได้ลองทำแล้ว
ก็จริงเหมือนกันที่ได้ทำแล้ว แต่ทำยังไม่ถึงจุดของมันคือความร้อนยังไม่สมดุลกัน ไฟมันก็เกิดขึ้นไม่ได้ ทั้งที่ความจริงไฟมันก็มีอยู่ อย่างนี้ก็เกิดความท้อแท้ขึ้นในใจของผู้ปฏิบัตินั้น ก็ละอันนี้ไปทำอันโน้นเรื่อยไป อันนี้ฉันใดก็ฉันนั้น
การปฏิบัตินั้น ปฏิบัติทางกายทางใจทั้งสองอย่าง มันต้องพร้อมกัน เพราะอะไร? เพราะพื้นเพมันเป็นคนมีกิเลสทั้งนั้น พระพุทธเจ้าก่อนที่จะเป็นพระพุทธเจ้า ท่านก็มีกิเลสแต่ท่านมีปัญญามากหลาย พระอรหันต์ก็เหมือนกัน เมื่อยังเป็นปุถุชนอยู่ ก็เหมือนกับเรา
เมื่อความอยากเกิดขึ้นมา เราก็ไม่รู้จัก เมื่อความไม่อยากเกิดขึ้นมา เราก็ไม่รู้จัก บางทีก็ร้อนใจ บางทีก็ดีใจ ถ้าใจเราไม่อยาก ก็ดีใจแบบหนึ่ง และวุ่นวายอีกแบบหนึ่ง ถ้าใจเราอยาก มันก็วุ่นวายอย่างหนึ่ง และดีใจอย่างหนึ่ง มันประสมประเสกันอยู่อย่างนี้
อันนี้คือปฏิปทาของผู้ปฏิบัติเรา
[อ่านใจธรรมชาติ] หลวงปู่ชา สุภัทโท หนังสือ หมวด: โพธิญาณ
-
 @ cae03c48:2a7d6671
2025-05-28 12:00:44
@ cae03c48:2a7d6671
2025-05-28 12:00:44Bitcoin Magazine

President Trump Supports Strategic Bitcoin Reserve Bill, Senator Lummis SaysToday at the Bitcoin 2025 Conference in Las Vegas, Nevada, US Senator Cynthia Lummis of Wyoming, Senator Marsha Blackburn of Tennessee, and Senator Jim Justice of West Virginia, took the stage to give updates on federal and state level Bitcoin adoption in the United States.
JUST IN:
 Senator Cynthia Lummis said US military generals are "big supporters" of a Strategic Bitcoin Reserve for economic power. pic.twitter.com/2RPMV3tbdA
Senator Cynthia Lummis said US military generals are "big supporters" of a Strategic Bitcoin Reserve for economic power. pic.twitter.com/2RPMV3tbdA— Bitcoin Magazine (@BitcoinMagazine) May 27, 2025
Cynthia Lummis announced that President Donald Trump is supportive of her Strategic Bitcoin Reserve Act, which would see the United States purchase 1,000,000 BTC, among other pro-Bitcoin and stablecoin legislation.
“President Trump supports the bill,” she stated. “And he has a team in the White House working on digital assets — everything from stablecoins to market structure to Bitcoin Strategic Reserve. And they will probably roll out in that order.”
“States have always been the incubators of innovation,” Lummis said. “Senator Justice was the Governor of West Virginia, Senator Blackburn will be the next Governor of Tennessee. The states are where the innovation is occurring.”
“So you have Arizona, Texas and New Hampshire that passed Strategic Bitcoin Reserve bills this year,” she continued. “30 states consider Strategic Bitcoin Reserves. We have the United Arab Emirates purchasing Bitcoin through American exchange traded funds — that’s good for America.”

Senator Blackburn echoed Lummis’ statements, sharing her thoughts on how other countries will follow the United States in their adoption of Bitcoin.
“Many of our allies follow what we do,” Blackburn said. “Everybody wants to be a part of of our market, they want to be a part of our trade. And they will follow what we do. And as Senator Lummis said, we already see countries that are establishing these reserves. So it is vitally important that we hold this as a portion of our reserves.”
Justice emphasized that to be successful, “we have got to get the economics right. Many people ask me many times as Governor, ‘what’s the most important thing you do?’ And I’ll promise you this, it’s all about the economics.”
Justice then went on to explain that when the average, everyday person is using Bitcoin to purchase their necessities, that legislation will start “happening at light speed”, because politicians want to get re-elected and therefore must follow the will of the people.

You can watch the full panel discussion and the rest of the Bitcoin 2025 Conference Industry Day below:
This post President Trump Supports Strategic Bitcoin Reserve Bill, Senator Lummis Says first appeared on Bitcoin Magazine and is written by Nik.
-
 @ a4a6b584:1e05b95b
2025-01-02 18:13:31
@ a4a6b584:1e05b95b
2025-01-02 18:13:31The Four-Layer Framework
Layer 1: Zoom Out

Start by looking at the big picture. What’s the subject about, and why does it matter? Focus on the overarching ideas and how they fit together. Think of this as the 30,000-foot view—it’s about understanding the "why" and "how" before diving into the "what."
Example: If you’re learning programming, start by understanding that it’s about giving logical instructions to computers to solve problems.
- Tip: Keep it simple. Summarize the subject in one or two sentences and avoid getting bogged down in specifics at this stage.
Once you have the big picture in mind, it’s time to start breaking it down.
Layer 2: Categorize and Connect

Now it’s time to break the subject into categories—like creating branches on a tree. This helps your brain organize information logically and see connections between ideas.
Example: Studying biology? Group concepts into categories like cells, genetics, and ecosystems.
- Tip: Use headings or labels to group similar ideas. Jot these down in a list or simple diagram to keep track.
With your categories in place, you’re ready to dive into the details that bring them to life.
Layer 3: Master the Details

Once you’ve mapped out the main categories, you’re ready to dive deeper. This is where you learn the nuts and bolts—like formulas, specific techniques, or key terminology. These details make the subject practical and actionable.
Example: In programming, this might mean learning the syntax for loops, conditionals, or functions in your chosen language.
- Tip: Focus on details that clarify the categories from Layer 2. Skip anything that doesn’t add to your understanding.
Now that you’ve mastered the essentials, you can expand your knowledge to include extra material.
Layer 4: Expand Your Horizons

Finally, move on to the extra material—less critical facts, trivia, or edge cases. While these aren’t essential to mastering the subject, they can be useful in specialized discussions or exams.
Example: Learn about rare programming quirks or historical trivia about a language’s development.
- Tip: Spend minimal time here unless it’s necessary for your goals. It’s okay to skim if you’re short on time.
Pro Tips for Better Learning
1. Use Active Recall and Spaced Repetition
Test yourself without looking at notes. Review what you’ve learned at increasing intervals—like after a day, a week, and a month. This strengthens memory by forcing your brain to actively retrieve information.
2. Map It Out
Create visual aids like diagrams or concept maps to clarify relationships between ideas. These are particularly helpful for organizing categories in Layer 2.
3. Teach What You Learn
Explain the subject to someone else as if they’re hearing it for the first time. Teaching exposes any gaps in your understanding and helps reinforce the material.
4. Engage with LLMs and Discuss Concepts
Take advantage of tools like ChatGPT or similar large language models to explore your topic in greater depth. Use these tools to:
- Ask specific questions to clarify confusing points.
- Engage in discussions to simulate real-world applications of the subject.
- Generate examples or analogies that deepen your understanding.Tip: Use LLMs as a study partner, but don’t rely solely on them. Combine these insights with your own critical thinking to develop a well-rounded perspective.
Get Started
Ready to try the Four-Layer Method? Take 15 minutes today to map out the big picture of a topic you’re curious about—what’s it all about, and why does it matter? By building your understanding step by step, you’ll master the subject with less stress and more confidence.
-
 @ fd208ee8:0fd927c1
2024-12-26 07:02:59
@ fd208ee8:0fd927c1
2024-12-26 07:02:59I just read this, and found it enlightening.
Jung... notes that intelligence can be seen as problem solving at an everyday level..., whereas creativity may represent problem solving for less common issues
Other studies have used metaphor creation as a creativity measure instead of divergent thinking and a spectrum of CHC components instead of just g and have found much higher relationships between creativity and intelligence than past studies
https://www.mdpi.com/2079-3200/3/3/59
I'm unusually intelligent (Who isn't?), but I'm much more creative, than intelligent, and I think that confuses people. The ability to apply intelligence, to solve completely novel problems, on the fly, is something IQ tests don't even claim to measure. They just claim a correlation.
Creativity requires taking wild, mental leaps out into nothingness; simply trusting that your brain will land you safely. And this is why I've been at the forefront of massive innovation, over and over, but never got rich off of it.
I'm a starving autist.
Zaps are the first time I've ever made money directly, for solving novel problems. Companies don't do this because there is a span of time between providing a solution and the solution being implemented, and the person building the implementation (or their boss) receives all the credit for the existence of the solution. At best, you can hope to get pawned off with a small bonus.
Nobody can remember who came up with the solution, originally, and that person might not even be there, anymore, and probably never filed a patent, and may have no idea that their idea has even been built. They just run across it, later, in a tech magazine or museum, and say, "Well, will you look at that! Someone actually went and built it! Isn't that nice!"
Universities at least had the idea of cementing novel solutions in academic papers, but that: 1) only works if you're an academic, and at a university, 2) is an incredibly slow process, not appropriate for a truly innovative field, 3) leads to manifestations of perverse incentives and biased research frameworks, coming from 'publish or perish' policies.
But I think long-form notes and zaps solve for this problem. #Alexandria, especially, is being built to cater to this long-suffering class of chronic underachievers. It leaves a written, public, time-stamped record of Clever Ideas We Have Had.
Because they are clever, the ideas. And we have had them.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:22
@ 04c915da:3dfbecc9
2025-05-20 15:50:22There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 39cc53c9:27168656
2025-05-27 09:21:40
@ 39cc53c9:27168656
2025-05-27 09:21:40“The future is there... staring back at us. Trying to make sense of the fiction we will have become.” — William Gibson.
This month is the 4th anniversary of kycnot.me. Thank you for being here.
Fifteen years ago, Satoshi Nakamoto introduced Bitcoin, a peer-to-peer electronic cash system: a decentralized currency free from government and institutional control. Nakamoto's whitepaper showed a vision for a financial system based on trustless transactions, secured by cryptography. Some time forward and KYC (Know Your Customer), AML (Anti-Money Laundering), and CTF (Counter-Terrorism Financing) regulations started to come into play.
What a paradox: to engage with a system designed for decentralization, privacy, and independence, we are forced to give away our personal details. Using Bitcoin in the economy requires revealing your identity, not just to the party you interact with, but also to third parties who must track and report the interaction. You are forced to give sensitive data to entities you don't, can't, and shouldn't trust. Information can never be kept 100% safe; there's always a risk. Information is power, who knows about you has control over you.
Information asymmetry creates imbalances of power. When entities have detailed knowledge about individuals, they can manipulate, influence, or exploit this information to their advantage. The accumulation of personal data by corporations and governments enables extensive surveillances.
Such practices, moreover, exclude individuals from traditional economic systems if their documentation doesn't meet arbitrary standards, reinforcing a dystopian divide. Small businesses are similarly burdened by the costs of implementing these regulations, hindering free market competition^1:
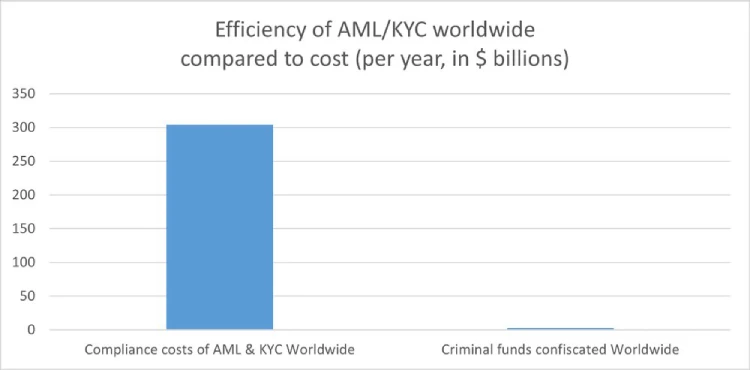
How will they keep this information safe? Why do they need my identity? Why do they force businesses to enforce such regulations? It's always for your safety, to protect you from the "bad". Your life is perpetually in danger: terrorists, money launderers, villains... so the government steps in to save us.
‟Hush now, baby, baby, don't you cry Mamma's gonna make all of your nightmares come true Mamma's gonna put all of her fears into you Mamma's gonna keep you right here, under her wing She won't let you fly, but she might let you sing Mamma's gonna keep baby cosy and warm” — Mother, Pink Floyd
We must resist any attack on our privacy and freedom. To do this, we must collaborate.
If you have a service, refuse to ask for KYC; find a way. Accept cryptocurrencies like Bitcoin and Monero. Commit to circular economies. Remove the need to go through the FIAT system. People need fiat money to use most services, but we can change that.
If you're a user, donate to and prefer using services that accept such currencies. Encourage your friends to accept cryptocurrencies as well. Boycott FIAT system to the greatest extent you possibly can.
This may sound utopian, but it can be achieved. This movement can't be stopped. Go kick the hornet's nest.
“We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.” — Eric Hughes, A Cypherpunk's Manifesto
The anniversary
Four years ago, I began exploring ways to use crypto without KYC. I bookmarked a few favorite services and thought sharing them to the world might be useful. That was the first version of kycnot.me — a simple list of about 15 services. Since then, I've added services, rewritten it three times, and improved it to what it is now.
kycnot.me has remained 100% independent and 100% open source^2 all these years. I've received offers to buy the site, all of which I have declined and will continue to decline. It has been DDoS attacked many times, but we made it through. I have also rewritten the whole site almost once per year (three times in four years).
The code and scoring algorithm are open source (contributions are welcome) and I can't arbitrarly change a service's score without adding or removing attributes, making any arbitrary alterations obvious if they were fake. You can even see the score summary for any service's score.
I'm a one-person team, dedicating my free time to this project. I hope to keep doing so for many more years. Again, thank you for being part of this.
-
 @ 21810ca8:f2e8341e
2025-05-28 08:10:53
@ 21810ca8:f2e8341e
2025-05-28 08:10:53Ich bin neu bei Nostr und versuche mich hier rein zu fuchsen. Kann das einer sehen? Und dann habe ich noch viele Fragen
Gibt es gute Marktplätze wie ebay oder ebay kleinanzeigen wo man stink normale dinge und kram von zuhause gegen sat verkaufen kann.
-
 @ fe32298e:20516265
2024-12-16 20:59:13
@ fe32298e:20516265
2024-12-16 20:59:13Today I learned how to install NVapi to monitor my GPUs in Home Assistant.
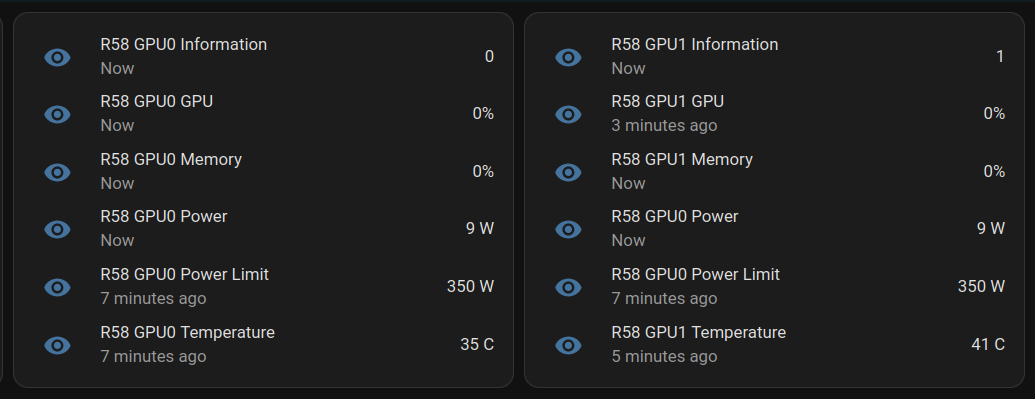
NVApi is a lightweight API designed for monitoring NVIDIA GPU utilization and enabling automated power management. It provides real-time GPU metrics, supports integration with tools like Home Assistant, and offers flexible power management and PCIe link speed management based on workload and thermal conditions.
- GPU Utilization Monitoring: Utilization, memory usage, temperature, fan speed, and power consumption.
- Automated Power Limiting: Adjusts power limits dynamically based on temperature thresholds and total power caps, configurable per GPU or globally.
- Cross-GPU Coordination: Total power budget applies across multiple GPUs in the same system.
- PCIe Link Speed Management: Controls minimum and maximum PCIe link speeds with idle thresholds for power optimization.
- Home Assistant Integration: Uses the built-in RESTful platform and template sensors.
Getting the Data
sudo apt install golang-go git clone https://github.com/sammcj/NVApi.git cd NVapi go run main.go -port 9999 -rate 1 curl http://localhost:9999/gpuResponse for a single GPU:
[ { "index": 0, "name": "NVIDIA GeForce RTX 4090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 16, "power_limit_watts": 450, "memory_total_gb": 23.99, "memory_used_gb": 0.46, "memory_free_gb": 23.52, "memory_usage_percent": 2, "temperature": 38, "processes": [], "pcie_link_state": "not managed" } ]Response for multiple GPUs:
[ { "index": 0, "name": "NVIDIA GeForce RTX 3090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 14, "power_limit_watts": 350, "memory_total_gb": 24, "memory_used_gb": 0.43, "memory_free_gb": 23.57, "memory_usage_percent": 2, "temperature": 36, "processes": [], "pcie_link_state": "not managed" }, { "index": 1, "name": "NVIDIA RTX A4000", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 10, "power_limit_watts": 140, "memory_total_gb": 15.99, "memory_used_gb": 0.56, "memory_free_gb": 15.43, "memory_usage_percent": 3, "temperature": 41, "processes": [], "pcie_link_state": "not managed" } ]Start at Boot
Create
/etc/systemd/system/nvapi.service:``` [Unit] Description=Run NVapi After=network.target
[Service] Type=simple Environment="GOPATH=/home/ansible/go" WorkingDirectory=/home/ansible/NVapi ExecStart=/usr/bin/go run main.go -port 9999 -rate 1 Restart=always User=ansible
Environment="GPU_TEMP_CHECK_INTERVAL=5"
Environment="GPU_TOTAL_POWER_CAP=400"
Environment="GPU_0_LOW_TEMP=40"
Environment="GPU_0_MEDIUM_TEMP=70"
Environment="GPU_0_LOW_TEMP_LIMIT=135"
Environment="GPU_0_MEDIUM_TEMP_LIMIT=120"
Environment="GPU_0_HIGH_TEMP_LIMIT=100"
Environment="GPU_1_LOW_TEMP=45"
Environment="GPU_1_MEDIUM_TEMP=75"
Environment="GPU_1_LOW_TEMP_LIMIT=140"
Environment="GPU_1_MEDIUM_TEMP_LIMIT=125"
Environment="GPU_1_HIGH_TEMP_LIMIT=110"
[Install] WantedBy=multi-user.target ```
Home Assistant
Add to Home Assistant
configuration.yamland restart HA (completely).For a single GPU, this works: ``` sensor: - platform: rest name: MYPC GPU Information resource: http://mypc:9999 method: GET headers: Content-Type: application/json value_template: "{{ value_json[0].index }}" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature scan_interval: 1 # seconds
- platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} GPU" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Memory" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Temperature" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'temperature') }}" unit_of_measurement: "°C" ```
For multiple GPUs: ``` rest: scan_interval: 1 resource: http://mypc:9999 sensor: - name: "MYPC GPU0 Information" value_template: "{{ value_json[0].index }}" json_attributes_path: "$.0" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature - name: "MYPC GPU1 Information" value_template: "{{ value_json[1].index }}" json_attributes_path: "$.1" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature
-
platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC GPU0 GPU" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC GPU0 Memory" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC GPU0 Power" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC GPU0 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC GPU0 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'temperature') }}" unit_of_measurement: "C"
-
platform: template sensors: mypc_gpu_1_gpu: friendly_name: "MYPC GPU1 GPU" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_memory: friendly_name: "MYPC GPU1 Memory" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_power: friendly_name: "MYPC GPU1 Power" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_1_power_limit: friendly_name: "MYPC GPU1 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_1_temperature: friendly_name: "MYPC GPU1 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'temperature') }}" unit_of_measurement: "C"
```
Basic entity card:
type: entities entities: - entity: sensor.mypc_gpu_0_gpu secondary_info: last-updated - entity: sensor.mypc_gpu_0_memory secondary_info: last-updated - entity: sensor.mypc_gpu_0_power secondary_info: last-updated - entity: sensor.mypc_gpu_0_power_limit secondary_info: last-updated - entity: sensor.mypc_gpu_0_temperature secondary_info: last-updatedAnsible Role
```
-
name: install go become: true package: name: golang-go state: present
-
name: git clone git: repo: "https://github.com/sammcj/NVApi.git" dest: "/home/ansible/NVapi" update: yes force: true
go run main.go -port 9999 -rate 1
-
name: install systemd service become: true copy: src: nvapi.service dest: /etc/systemd/system/nvapi.service
-
name: Reload systemd daemons, enable, and restart nvapi become: true systemd: name: nvapi daemon_reload: yes enabled: yes state: restarted ```
-
 @ cff1720e:15c7e2b2
2025-05-28 11:18:23
@ cff1720e:15c7e2b2
2025-05-28 11:18:23Liebe Anwender,\ \ diesmal beginnen die Neuigkeiten schon beim Titel und der Anrede. Unsere Worte bestimmen unser Denken, und daher war die Korrektur wichtiger als sie zunächst erscheint, denn bei Pareto gibt es die klassische Trennung zwischen Autor und Leser nicht mehr. Cocreation heißt unser Konzept, jeder kann publizieren, kommentieren, honorieren und distribuieren. Mag das bei Blogtexten derzeit noch nicht selbstverständlich sein, so ist das bei Bildern längst die Norm.

“Ein Bild sagt mehr als tausend Worte” beschreibt die Wirkung visueller Kommunikation. Deshalb haben wir nach dem Blogtext nun mit Bildern eine neue Content-Kategorie eingeführt. Natürlich auch hier mit den bekannten Funktionen der Interaktion wie like, repost und zap. Es gibt derzeit eine Gliederung in 4 Feeds, Gefolgt (für Nostr-User verfügbar), Memes und Kunst (gefiltert nach entsprechenden Tags) und Pareto für alles andere.
Jeder Nostr-User hat die Möglichkeit eigene Bilder hochzuladen, zu taggen, sowie mit einem Titel und Untertext zu versehen. “Everyone is a creator” war noch nie leichter, probiert es einfach aus! Noch kein Nostr-Profil und trotzdem interessiert? Kein Problem, bitte Informationen zu originellen Bildquellen oder Interesse an Mitwirkung per Mail senden an pictures@pareto.space
Leicht ist es auch die Pareto-Inhalte zu erhalten und konsumieren, man braucht weder einen Account noch spezielle Apps. Jeder hat bereits die entsprechenden Voraussetzungen, hier ein paar Beispiele.\ \ Newsletter per Mail (Die Friedenstaube)\ hier abonnieren\ \ In Telegram lesen -> hier unsere Kanäle\ https://t.me/pareto_artikel \ https://t.me/friedenstaube_artikel \ \ Als Feed in einem Feed-Reader \ https://pareto.space/atom/feed.xml \ https://pareto.space/atom/de_feed.xml \ https://pareto.space/atom/en_feed.xml
Fügt in Eure Artikel bitte am Anfang / Ende einen Hinweis auf den Pareto-Client ein, andere Clients unterstützen nicht alle Features. Das ist ein Service-Hinweis zur besseren Lesbarkeit “Dieser Beitrag wurde mit dem Pareto-Client geschrieben.” Ebenso ist ein Hinweis auf Onboarding bei Nostr nützlich: neue Nostr-User können euch liken und zappen: not yet on Nostr and want the full experience? Easy onboarding via Start.\ \ Das Pareto-Team baut den “Marktplatz der Ideen” und hat dabei schon viel erreicht. Feedback und Mitarbeit hilft uns damit noch schneller voranzukommen, wir bedanken uns für Eure Unterstützung.\ team@pareto.space \ https://pareto.space \ https://geyser.fund/project/pareto?hero=1c1b8e487090
-
 @ eb0157af:77ab6c55
2025-05-28 10:01:29
@ eb0157af:77ab6c55
2025-05-28 10:01:29Michigan lawmakers are unveiling a comprehensive strategy to regulate Bitcoin and cryptocurrencies.
On May 21, Republican Representative Bill Schuette introduced House Bill 4510, a proposal to amend the Michigan Public Employee Retirement System Investment Act. The legislation would allow the state treasurer, currently Rachael Eubanks, to diversify the state’s investments by including cryptocurrencies with an average market capitalization of over $250 million in the past calendar year.
Under current criteria, Bitcoin (BTC) and Ether (ETH) are the only cryptocurrencies that meet these selection standards. The proposal specifies that any investment in digital assets must be made through exchange-traded products (spot ETFs) issued by registered investment companies.
Anti-CBDC legislation
Republican Representative Bryan Posthumus is leading the bipartisan initiative behind the second bill, HB 4511, which establishes protections for cryptocurrency holders. The proposal prohibits Michigan from implementing crypto bans or imposing licensing requirements on digital asset holders.
Another key aspect of the legislation is a ban on state officials from supporting or promoting a potential federal central bank digital currency (CBDC). The definition includes the issuance of memorandums or official statements endorsing CBDC proposals related to testing, adoption, or implementation.
Mining and redevelopment of abandoned sites
The third bill, HB 4512, is a proposal led by Democratic Representative Mike McFall for a bipartisan group. This initiative would establish a Bitcoin mining program allowing operators to use abandoned oil and natural gas sites.
The program calls for the appointment of a supervisor tasked with assessing the site’s remaining productive potential, identifying the last operator, and determining the length of abandonment. Prospective participants would need to submit detailed legal documentation of their organizational structure, demonstrate operational expertise in mining, and provide profitability breakeven estimates for their ventures.
The fourth and final bill, HB 4513, also introduced by the bipartisan group led by McFall, focuses on the fiscal aspect of the HB 4512 initiative. The proposal would amend Michigan’s income tax laws to include proceeds generated from the proposed Bitcoin mining program.
The post Michigan: four bills on pension funds, CBDCs, and mining appeared first on Atlas21.
-
 @ c3b2802b:4850599c
2025-05-26 07:57:44
@ c3b2802b:4850599c
2025-05-26 07:57:44Knapp 20 Millionen Menschen im Land sind heute in Deutschland in Genossenschaften tätig, welche eine Alternative zum nicht zukunftsfähigen Abwärtsstrudel von global agierenden Wirtschafts- und Finanzplayern mit ihren Kriegs- und Krisenplänen darstellen. Und kaum bemerkt findet derzeit ein stürmisches Wachstum der Genossenschaftsbewegung statt.
Nach Informationen des Deutschen Genossenschafts- und Raiffeisenverbandes stieg während der Multikrise der vergangenen 5 Jahre im Laufe nur einen Jahres (vom Jahresbericht 2023 zum Jahresbericht 2024) die Zahl der Energiegenossenschaften von 877 auf 951 an, die von Konsum- und Dienstleistungsgenossenschaften von 440 auf 510 und die von gewerblichen Genossenschaften von 1.372 auf 1.419.
Wer das Gejammer von „Wirtschaftsweisen“ über zu geringe Wachstumsraten bei ethisch fragwürdigen Indikatoren einer wünschenswerten Gesellschaft wie dem BIP (Brutto-Inland-Produkt) im Ohr hat, könnte bereits beim Überschlagen des Anstiegs bei den oben genannten Zahlen die These gestützt sehen, dass der Strukturwandel hin zur Regionalgesellschaft bereits in vollem Gang ist.
Wenn Sie sich für die Aufbruchstimmung und den frischen Wind insbesondere bei den neu gegründeten Genossenschaften interessieren, schauen sie gern einmal auf die Plattform einer jungen Genossenschaft, welche „Menschlich Wirtschaften“ in ihrer Satzung zum Ziel erklärt hat.
Und sollten Sie Mitte Juni eine Reise an die Ostsee attraktiv finden, kommen Sie gern zum Genossenschaftstreffen vom 13. bis 15. Juni 2025 in Poppendorf bei Rostock. Dort dürfen Sie nicht nur einen Einblick in die aktuellen Baustellen und ersten Erfolge unserer bundesweit aktiven Genossenschaft erwarten, sondern auch ein buntes Kulturprogramm im Rahmen eines kleinen Festivals und ein Zusammensein mit Pionieren der Regionalgesellschaft!
Das Titelbild zeigt ein Menschlich Wirtschaften Domizil in Stralsund. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Was charakterisiert eine Genossenschaft?
-
 @ 3f770d65:7a745b24
2025-04-21 00:15:06
@ 3f770d65:7a745b24
2025-04-21 00:15:06At the recent Launch Music Festival and Conference in Lancaster, PA, featuring over 120 musicians across three days, I volunteered my time with Tunestr and Phantom Power Music's initiative to introduce artists to Bitcoin, Nostr, and the value-for-value model. Tunestr sponsored a stage, live-streaming 21 bands to platforms like Tunestr.io, Fountain.fm and other Nostr/Podcasting 2.0 apps and on-boarding as many others as possible at our conference booth. You may have seen me spamming about this over the last few days.
V4V Earnings
Day 1: 180,000 sats
Day 2: 300,000 sats
Day 3: Over 500,000 sats
Who?
Here are the artists that were on-boarded to Fountain and were live streaming on the Value-for-Value stage:
nostr:npub1cruu4z0hwg7n3r2k7262vx8jsmra3xpku85frl5fnfvrwz7rd7mq7e403w nostr:npub12xeh3n7w8700z4tpd6xlhlvg4vtg4pvpxd584ll5sva539tutc3q0tn3tz nostr:npub1rc80p4v60uzfhvdgxemhvcqnzdj7t59xujxdy0lcjxml3uwdezyqtrpe0j @npub16vxr4pc2ww3yaez9q4s53zkejjfd0djs9lfe55sjhnqkh nostr:npub10uspdzg4fl7md95mqnjszxx82ckdly8ezac0t3s06a0gsf4f3lys8ypeak nostr:npub1gnyzexr40qut0za2c4a0x27p4e3qc22wekhcw3uvdx8mwa3pen0s9z90wk nostr:npub13qrrw2h4z52m7jh0spefrwtysl4psfkfv6j4j672se5hkhvtyw7qu0almy nostr:npub1p0kuqxxw2mxczc90vcurvfq7ljuw2394kkqk6gqnn2cq0y9eq5nq87jtkk nostr:npub182kq0sdp7chm67uq58cf4vvl3lk37z8mm5k5067xe09fqqaaxjsqlcazej nostr:npub162hr8kd96vxlanvggl08hmyy37qsn8ehgj7za7squl83um56epnswkr399 nostr:npub17jzk5ex2rafres09c4dnn5mm00eejye6nrurnlla6yn22zcpl7vqg6vhvx nostr:npub176rnksulheuanfx8y8cr2mrth4lh33svvpztggjjm6j2pqw6m56sq7s9vz nostr:npub1akv7t7xpalhsc4nseljs0c886jzuhq8u42qdcwvu972f3mme9tjsgp5xxk nostr:npub18x0gv872489lrczp9d9m4hx59r754x7p9rg2jkgvt7ul3kuqewtqsssn24
Many more musicians were on-boarded to Fountain, however, we were unable to obtain all of their npubs.
THANK YOU TO ALL ZAPPERS AND BOOSTERS!
Musicians “Get It”
My key takeaway was the musicians' absolute understanding that the current digital landscape along with legacy social media is failing them. Every artist I spoke with recognized how algorithms hinder fan connection and how gatekeepers prevent fair compensation for their work. They all use Spotify, but they only do so out of necessity. They felt the music industry is primed for both a social and monetary revolution. Some of them were even speaking my language…
Because of this, concepts like decentralization, censorship resistance, owning your content, and controlling your social graph weren't just understood by them, they were instantly embraced. The excitement was real; they immediately saw the potential and agreed with me. Bitcoin and Nostr felt genuinely punk rock and that helped a lot of them identify with what we were offering them.
The Tools and the Issues
While the Nostr ecosystem offers a wide variety of tools, we focused on introducing three key applications at this event to keep things clear for newcomers:
- Fountain, with a music focus, was the primary tool for onboarding attendees onto Nostr. Fountain was also chosen thanks to Fountain’s built-in Lightning wallet.
- Primal, as a social alternative, was demonstrated to show how users can take their Nostr identity and content seamlessly between different applications.
- Tunestr.io, lastly was showcased for its live video streaming capabilities.
Although we highlighted these three, we did inform attendees about the broader range of available apps and pointed them to
nostrapps.comif they wanted to explore further, aiming to educate without overwhelming them.This review highlights several UX issues with the Fountain app, particularly concerning profile updates, wallet functionality, and user discovery. While Fountain does work well, these minor hiccups make it extremely hard for on-boarding and education.
- Profile Issues:
- When a user edits their profile (e.g., Username/Nostr address, Lightning address) either during or after creation, the changes don't appear to consistently update across the app or sync correctly with Nostr relays.
- Specifically, the main profile display continues to show the old default Username/Nostr address and Lightning address inside Fountain and on other Nostr clients.
- However, the updated Username/Nostr address does appear on https://fountain.fm (chosen-username@fountain.fm) and is visible within the "Edit Profile" screen itself in the app.
- This inconsistency is confusing for users, as they see their updated information in some places but not on their main public-facing profile within the app. I confirmed this by observing a new user sign up and edit their username – the edit screen showed the new name, but the profile display in Fountain did not update and we did not see it inside Primal, Damus, Amethyst, etc.
- Wallet Limitations:
- The app's built-in wallet cannot scan Lightning address QR codes to initiate payments.
- This caused problems during the event where users imported Bitcoin from Azte.co vouchers into their Fountain wallets. When they tried to Zap a band by scanning a QR code on the live tally board, Fountain displayed an error message stating the invoice or QR code was invalid.
- While suggesting musicians install Primal as a second Nostr app was a potential fix for the QR code issue, (and I mentioned it to some), the burden of onboarding users onto two separate applications, potentially managing two different wallets, and explaining which one works for specific tasks creates a confusing and frustrating user experience.
- Search Difficulties:
- Finding other users within the Fountain app is challenging. I was unable to find profiles from brand new users by entering their chosen Fountain username.
- To find a new user, I had to resort to visiting their profile on the web (fountain.fm/username) to retrieve their npub. Then, open Primal and follow them. Finally, when searching for their username, since I was now following them, I was able to find their profile.
- This search issue is compounded by the profile syncing problem mentioned earlier, as even if found via other clients, their displayed information is outdated.
- Searching for the event to Boost/Zap inside Fountain was harder than it should have been the first two days as the live stream did not appear at the top of the screen inside the tap. This was resolved on the third day of the event.
Improving the Onboarding Experience
To better support user growth, educators and on-boarders need more feature complete and user-friendly applications. I love our developers and I will always sing their praises from the highest mountain tops, however I also recognize that the current tools present challenges that hinder a smooth onboarding experience.
One potential approach explored was guiding users to use Primal (including its built-in wallet) in conjunction with Wavlake via Nostr Wallet Connect (NWC). While this could facilitate certain functions like music streaming, zaps, and QR code scanning (which require both Primal and Wavlake apps), Wavlake itself has usability issues. These include inconsistent or separate profiles between web and mobile apps, persistent "Login" buttons even when logged in on the mobile app with a Nostr identity, and the minor inconvenience of needing two separate applications. Although NWC setup is relatively easy and helps streamline the process, the need to switch between apps adds complexity, especially when time is limited and we’re aiming to showcase the benefits of this new system.
Ultimately, we need applications that are more feature-complete and intuitive for mainstream users to improve the onboarding experience significantly.
Looking forward to the future
I anticipate that most of these issues will be resolved when these applications address them in the near future. Specifically, this would involve Fountain fixing its profile issues and integrating Nostr Wallet Connect (NWC) to allow users to utilize their Primal wallet, or by enabling the scanning of QR codes that pay out to Lightning addresses. Alternatively, if Wavlake resolves the consistency problems mentioned earlier, this would also significantly improve the situation giving us two viable solutions for musicians.
My ideal onboarding event experience would involve having all the previously mentioned issues resolved. Additionally, I would love to see every attendee receive a $5 or $10 voucher to help them start engaging with value-for-value, rather than just the limited number we distributed recently. The goal is to have everyone actively zapping and sending Bitcoin throughout the event. Maybe we can find a large sponsor to facilitate this in the future?
What's particularly exciting is the Launch conference's strong interest in integrating value-for-value across their entire program for all musicians and speakers at their next event in Dallas, Texas, coming later this fall. This presents a significant opportunity to onboard over 100+ musicians to Bitcoin and Nostr, which in turn will help onboard their fans and supporters.
We need significantly more zaps and more zappers! It's unreasonable to expect the same dedicated individuals to continuously support new users; they are being bled dry. A shift is needed towards more people using bitcoin for everyday transactions, treating it as money. This brings me back to my ideal onboarding experience: securing a sponsor to essentially give participants bitcoin funds specifically for zapping and tipping artists. This method serves as a practical lesson in using bitcoin as money and showcases the value-for-value principle from the outset.
-
 @ 69eea734:4ae31ae6
2025-05-26 01:15:05
@ 69eea734:4ae31ae6
2025-05-26 01:15:05Dies ist der Anfang einer Serie, die ich schreiben möchte. Sie handelt von etwas, das wir verloren haben, und das dennoch, in Teilen, in uns weiterlebt.
Wen meine ich mit dem “wir”? Das Wir kann schnell problematisch werden, wenn man meint für andere zu sprechen, und dann erkennen muss, falsche Annahmen gemacht zu haben.
Als ich diesen Satz schrieb, hatte ich diejenigen von uns im Hinterkopf, die in einer westlichen Industriegesellschaft aufgewachsen sind. Der Verlust ist etwas, das ich spüre, und dem reale Geschehnisse mit zugrunde liegen. Eine Art Sehnsucht wird stärker, wenn ich von bestimmten Ereignissen lese, bei denen Menschen gewaltsam von dem getrennt wurden, das sie bis dahin gehalten und ernährt hatte: Dem Land, zu dem sie gehörten.
Worüber ich schreiben möchte, das sind die Commons. Ein weites Feld. Commons, das kann Allmende heißen oder Gemeingüter.
Es geht dabei aber nicht nur um das, was gemeinsam genutzt wird, sondern auch um das Soziale darum herum — wie sich eine Gruppe selbst organisiert, und dabei den Mitgliedern und dem Gemeingut gerecht wird
Es ist eines jener Konzepte, denen mit einer einfachen Definition nicht gut gedient ist. Es geht eher darum, ein Gefühl dafür zu bekommen, sich ihm anzunähern, eine Beziehung aufzubauen. Wenn das gelingt, dann ist man an einer Art neuem Ort, einer neuen (und gleichzeitig alten) Sichtweise angekommen, die man nicht mehr verliert. Und gleichzeitig Teil einer Gemeinschaft geworden.
Zum Commons gehören Personen und das Commoning. Subjekte und ein Verb. Hinzu kommen die Resourcen, die gemeinsam betreut werden. Also Subjekt, Verb, Objekt. Hilfreicher ist es, die Ressourcen ebenfalls als Subjekte zu sehen. Beim ursprünglichen Commons stand der Commoner in einer partnerschaftlichen Beziehung zu dem Land, das seine Lebensgrundlage war. [1]
Die Commons bilden ein Gegengewicht zu Staat und Privatwirtschaft. Sie funktionieren nach einer anderen Logik, und wirken der kapitalistischen Forderung nach exponentiellem Wachstum, und der Vereinzelung der Menschen in der modernen Gesellschaft entgegen.
Mein Vorhaben ist, alle ein bis zwei Wochen einen kurzen Aufsatz zu schreiben, der einen Aspekt der Commons beleuchtet. Der deutsche Wikipedia-Eintrag gibt sehr gut wieder, wie vielschichtig das Thema ist.
Es könnte dabei in folgende Richtungen gehen:
- Geschichte der Enclosures (Einhegungen)
- Kämpfe indigener Kulturen und anarchischer Gemeinschaften
- Bemühungen, Commons und das Commoning in unserer westlichen Kulturn wiederzubeleben und zu fördern
- Das kollektive Trauma, das mit dem Verlust von Gemeingütern, insbesondere Land, verbunden ist
- Wie sich dies in jedem Einzelnen widerspiegelt
Ich schreibe dabei auch, um mir selbst über bestimmte Dinge klar zu werden. Ich bin mit zwei Commons-Bewegungen im Südwesten Englands verbunden, und diese Beziehungen sind nicht immer ganz einfach. Und doch würde ich mich nicht davon lösen wollen.
Warum schrieb ich davon, dass wir etwas verloren haben, wenn es die Commons doch gibt?
Eine bestimmte Lebensweise, die freien Zugang zu Wald und Acker- und Weideland garantierte, um sich zu ernähren und Holz und Torf zu sammeln, wurde mit den Einhegungen nach und nach zerstört. Während das Leben sicher sehr hart war — und sich zuvor innerhalb der Feudalherrschaft abspielte — sorgten über lange Zeit gewachsene Traditionen und Bräuche dafür, dass Menschen sich zugehörig und versorgt fühlten. Diese Art des Aufgehobenseins ging verloren, als die Landbewohner vertrieben wurden und sich in den Städten als Lohnarbeiter verdingen oder auswandern mussten.
Vor kurzem habe ich ein Buch namens The Traumatised Society gelesen, in dem Fred Harrison das Schicksal des englischen Naturdichters John Clare schildert, der direkt miterlebte, wie das Land eingegrenzt wurde und darüber verzweifelte. Besonders eindrücklich schreibt auch Alastair McIntosh in dem insgesamt sehr erstaunlichen und magischen Buch Soil and Soul über die schottische Version der Einhegungen, die Highland Clearances.
Solche Schilderungen lassen ahnen, wie gewaltsam die Menschen von ihrer früheren Lebensweise getrennt wurden. Später gingen England und andere europäische Mächte in ihren Kolonien ähnlich vor. Die erste Kolonisierung war die der eigenen Bevölkerung. Ich glaube, dass diese Vorgänge uns kollektiv geprägt haben, und wir die Commons brauchen, um den Folgen entgegenzuwirken.
Diese haben aber auch in ihren neueren Formen keinen leichten Stand.
Wie Silke Helfrich schrieb: “Commons existieren nicht in einer heilen Welt, sondern in einer commons-unfreundlichen Umgebung. Es ist daher wichtig, dass Commoners sich bewusst sind, welchen Schatz sie in den Händen halten, um ihn bewahren und entfalten zu können.”
Demnächst mehr...
\ [1] Der amerikanische Priester und Gelehrte Thomas Berry rief dazu auf, das Universum nicht als eine Ansammlung von Objekten zu sehen, sondern eine Gemeinschaft von Subjekten: The universe is a communion of subjects, not a collection of objects.
-
 @ 3770c235:16042bcc
2025-05-28 05:54:01
@ 3770c235:16042bcc
2025-05-28 05:54:01** Introduction: The Neon Pulse of Las Vegas
**It’s 2:30 AM on a Tuesday. The Strip hums with laughter, clinking glasses, and the occasional Elvis impersonator. A group of friends stumbles out of a nightclub, squinting under the glow of a Las Vegas billboard that screams, “Hungry? $5 Pancakes → 1 Block Right!” Ten minutes later, they’re drowning their late-night cravings in syrup.This isn’t luck—it’s Las Vegas billboards doing what they do best: working while the rest of the world sleeps. In a city where the party never stops, these glowing giants are the ultimate salespeople. Let’s dive into why Las Vegas billboards outshine traditional ads and how your business can ride their 24/7 energy wave.
** Why Las Vegas Billboards Never Take a Coffee Break
** 1. Tourists Don’t Have Bedtimes (and Neither Do Billboards)
- 42 million visitors flock to Vegas yearly. They’re sipping margaritas at noon, gambling at midnight, and shopping at 3 AM.
- Las Vegas billboards near hotspots like the Bellagio Fountains or Fremont Street catch eyes round the clock.Real Story:
A donut shop owner named Luis rented a billboard near the “Welcome to Vegas” sign. His message? “Jet Lagged? Sugar Fix Open 24/7!” Sales tripled—especially between 1 AM and 4 AM.** 2. You Can’t “Skip” a Billboard
** - Imagine this: You’re stuck in traffic on the Strip. Your phone’s dead. That Las Vegas billboard for air-conditioned massages? It’s your lifeline.
- Compare that to online ads: 47% of people skip them, and TikTok ads vanish in a scroll.- Vegas Thrives on Impulse
- Billboards tap into spontaneous decisions:
- “Let’s try that rooftop bar!”
- “Wait, free slot play? Let’s U-turn!”
- Traditional ads (like radio spots) fade fast. Billboards linger, nudging tourists to act now.
** 5 Reasons Your Business Needs a Vegas Billboard
** 1. Size Matters (And So Does Flash)
- Strip billboards can be taller than a 5-story building.
- Digital screens use LEDs so bright, they’re visible from space.Pro Tip:
A casino added fake “smoke” effects to their billboard for a Halloween promo. Traffic backed up for selfies—and bookings spiked.- No Language Barrier
- Vegas draws visitors from Tokyo, Berlin, São Paulo...
- A Las Vegas billboard with a giant cocktail emoji? Universal for “Drinks here!”
Case Study:
A Korean BBQ spot used a billboard of sizzling meat. No words. Just smoke visuals. Tourists followed the “aroma” straight to their door.- They’re Always in the Right Place, Right Time
- 6 AM: Joggers see smoothie ads.
- 3 PM: Pool partiers spot “Free Margarita” promos.
-
Midnight: Hangover clinics whisper, “We’ve got IVs.”
-
Instant Trust Boost
- A tiny online ad says “startup.” A glowing billboard says, “We’re Vegas royalty.”
Jake’s Win:
Jake’s tiny magic shop rented a billboard reading, “Real Tricks—Cheaper Than the Casino!” Tourists treated him like David Blaine.- QR Codes = Instant Customers
- “Scan for free parking!” → 1,000 scans in a weekend.
- “Tap to call a limo” → Rides booked before the light turns green.
** How to Make Your Vegas Billboard Irresistible
** Step 1: Claim Your Territory
- The Strip: Pricey but prime ($15k–$60k/month).
- Fremont Street: Quirky, cheaper ($5k–$20k), packed with partiers.
- Highway 15: Target road-trippers with “Almost There! Cold Beer Ahead!”Step 2: Keep It Stupid Simple
- Bad: “Experience Culinary Excellence at Our Artisanal Bistro!”
- Good: “24/7 Bacon Pancakes → Exit Here.”Maria’s Hack:
Maria’s tattoo parlor used a billboard with a flaming skull and three words: “Walk-Ins Welcome.” No phone number. “People just… show up,” she laughs.Step 3: Track Your Wins (Like a Vegas High Roller)
- QR Codes: “Scan for Free Slot Play!” → Track scans.
- Unique URLs: “Visit VegasPizza24.com” → Monitor traffic.
- Old-School: Count foot traffic. (“Did that bachelor party just roll in from our billboard? Yes.”)**FAQs ** 1. “How do I even measure if my billboard’s working? It’s not like online ads!”
Answer:
You’re right—it’s not just clicks and likes. But here’s how real businesses track success:
- QR Codes: Add a unique code like “Scan for Free Appetizer!” Track scans.
- Promo Codes: “Mention this billboard for 20% off!” (Works great for Uber drivers: “My passengers blurt it out mid-ride,” says driver Luis M.)
- Foot Traffic Spikes: Note sales surges after your ad goes live. A dispensary saw a 60% bump in visits after their “We’re Closer Than the Casino!” billboard.
- Social Media Tags: Encourage selfies with your billboard. A retro motel offered a free pool pass for tagged photos. Their Instagram exploded.- “Aren’t billboards old-school? My Gen Z customers live on TikTok!”
Answer:
Billboards in Vegas are anything but old-school. Here’s why: - Hybrid Campaigns: Pair billboards with geofenced mobile ads. Example: A billboard for a pool party says, “Scan to Pre-Order Drinks.” Users nearby get a TikTok-style ad on their phone.
- Instagrammable Designs: Quirky billboards go viral. The “Welcome to Vegas” sign is the most Instagrammed spot in the city. Mimic that vibe!
- Influencer Collabs: Pay a Vegas influencer to pose with your billboard. Their followers will hunt it down like a scavenger hunt.
Real Story:
A vintage clothing store’s billboard (“Find Your Retro Vibe → 2 Blocks East”) became a TikTok trend after a local influencer did a “thrift haul” video there.** 3. “What’s the biggest mistake businesses make with Vegas billboards?”
** Answer:
Trying to cram in too much info! Drivers have 5–7 seconds to read your ad. Avoid:
- Text Overload: “Grand Opening! 50% Off! Open 24/7! Call Now!” → Too much!
- Bland Designs: Gray text on a gray background? Yawn.
- Ignoring Locals: Tourists are 70% of viewers, but locals matter too. A gym’s billboard said, “Tired of Tourists? Work Out in Peace.” Memberships spiked.Fix It:
- Use 7 words max.
- Bold colors (red, yellow, neon pink).
- Add a clear call to action: “Turn Right Now!” or “Scan for Free Parking.”- “Do I need a permit? What if my ad gets rejected?”
Answer:
Yep, permits are a thing. The city bans: - Flashing Lights Near Residences: No strobes in suburban areas.
- Certain Content: No swear words, adult themes, or political fights.
How to Avoid Rejection:
- Work with local Outdoor Advertising companies—they know the rules.
- Submit designs early. One pizza joint’s ad was flagged for a pepperoni slice deemed “too suggestive.” They swapped it to a cheese pull… and it got approved.Conclusion: Let Your Business Shine All Night Long
At 5 AM, as the sun peeks over the desert, the Las Vegas billboards keep glowing. They’ve sold midnight pancakes, inspired shotgun weddings, and even talked someone out of a questionable tattoo (“Wait! Our Parlor’s Better → Next Exit”).These aren’t just ads—they’re part of Vegas’ heartbeat. So whether you’re slinging sushi, massages, or monster truck rides, remember: In a city that never sleeps, your billboard shouldn’t either.
Ready to Light Up the Night?
Find Las Vegas billboards near you today. And if you spot one that says, “Free High-Fives for Readers of This Article,” honk twice. It’s probably yours. -
 @ 866e0139:6a9334e5
2025-05-25 11:03:13
@ 866e0139:6a9334e5
2025-05-25 11:03:13Autor: Alexa Rodrian. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
„Triff niemals deine Idole“ heißt ein gängiger Ratschlag. In gewendeten Zeiten stehen zu dem die Werte auf dem Kopf – und manche Künstler mit ihnen. Die Worte, die aus manch ihrer Mündern kommen, wirken, als hätte eine fremde Hand sie auf deren Zunge gelegt.
Die Sängerin Alexa Rodrian erlebte bei der Verleihung des Deutschen Filmpreises einen solchen Moment der Desillusion. Es war der Auftritt des Liedermachers Wolf Biermann. Hören Sie hierzu Alexa Rodrians Text „Wolf Biermann und sein falscher Friede“.
https://soundcloud.com/radiomuenchen/wolf-biermann-und-sein-falscher-friede-von-alexa-rodrian
Dieser Beitrag erschien zuerst auf Radio München.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ fd06f542:8d6d54cd
2025-04-15 02:38:14
@ fd06f542:8d6d54cd
2025-04-15 02:38:14排名随机, 列表正在增加中。
Cody Tseng
jumble.social 的作者
https://jumble.social/users/npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl
- Running [ wss://nostr-relay.app ] (free & WoT) 💜⚡️
- Building 👨💻:
- https://github.com/CodyTseng/jumble
- https://github.com/CodyTseng/nostr-relay-tray
- https://github.com/CodyTseng/danmakustr
- https://github.com/CodyTseng/nostr-relay-nestjs
- https://github.com/CodyTseng/nostr-relay
- https://github.com/CodyTseng
阿甘
- @agan0
- 0xchat.com
- canidae40@coinos.io
- https://jumble.social/users/npub13zyg3zysfylqc6nwfgj2uvce5rtlck2u50vwtjhpn92wzyusprfsdl2rce
joomaen
- Follows you
- joomaen.com
-
95aebd@wallet.yakihonne.com
-
nobot
- https://joomaen.filegear-sg.me/
- https://jumble.social/users/npub1wlpfd84ymdx2rpvnqht7h2lkq5lazvkaejywrvtchlvn3geulfgqp74qq0
颜值精选官
- wasp@ok0.org
- 专注分享 各类 图片与视频,每日为你带来颜值盛宴,心动不止一点点。欢迎关注,一起发现更多美好!
- https://jumble.social/users/npub1d5ygkef6r0l7w29ek9l9c7hulsvdshms2qh74jp5qpfyad4g6h5s4ap6lz
6svjszwk
- 6svjszwk@ok0.org
- 83vEfErLivtS9to39i73ETeaPkCF5ejQFbExoM5Vc2FDLqSE5Ah6NbqN6JaWPQbMeJh2muDiHPEDjboCVFYkHk4dHitivVi
-
low-time-preference
-
anarcho-capitalism
-
libertarianism
-
bitcoin #monero
- https://jumble.social/users/npub1sxgnpqfyd5vjexj4j5tsgfc826ezyz2ywze3w8jchd0rcshw3k6svjszwk
𝘌𝘷𝘦𝘳𝘺𝘥𝘢𝘺 𝘔𝘰𝘳𝘯𝘪𝘯𝘨 𝘚𝘵𝘢𝘳
- everyday@iris.to
- 虽然现在对某些事情下结论还为时尚早,但是从趋势来看,邪恶抬头已经不可避免。
- 我们要做的就是坚持内心的那一份良知,与邪恶战斗到底。
- 黑暗森林时代,当好小透明。
- bc1q7tuckqhkwf4vgc64rsy3rxy5qy6pmdrgxewcww
- https://jumble.social/users/npub1j2pha2chpr0qsmj2f6w783200upa7dvqnnard7vn9l8tv86m7twqszmnke
nostr_cn_dev
npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm@npub.cash
Developed the following products: - NostrBridge, 网桥转发 - TaskQ5, 分布式多任务 - NostrHTTP, nostr to http - Postr, 匿名交友,匿名邮局 - nostrclient (Python client) . -nostrbook, (nostrbook.com) 用nostr在线写书 * https://www.duozhutuan.com nostrhttp demo * https://github.com/duozhutuan/NostrBridge * * https://jumble.social/users/npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm *
CXPLAY
- lightning@cxplay.org
- 😉很高兴遇到你, 你可以叫我 CX 或 CXPLAY, 这个名字没有特殊含义, 无需在意.
- ©本账号下所有内容如未经特殊声明均使用 CC BY-NC-SA 4.0 许可协议授权.
- 🌐如果您在 Fediverse 收到本账号的内容则说明您的实例已与 Mostr.pub 或 Momostr.pink Bridge 互联, 您所看到的账号为镜像, 所有账号内容正在跨网传递. 如有必要请检查原始页面.
- 🧑💻正在提供中文本地化(i10n): #Amethyst #Amber #Citrine #Soapbox #Ditto #Alby
- https://cx.ms/
https://jumble.social/users/npub1gd8e0xfkylc7v8c5a6hkpj4gelwwcy99jt90lqjseqjj2t253s2s6ch58h
w
- 0xchat的作者
- 0xchat@getalby.com
- Building for 0xchat
- https://www.0xchat.com/
- https://jumble.social/users/npub10td4yrp6cl9kmjp9x5yd7r8pm96a5j07lk5mtj2kw39qf8frpt8qm9x2wl
Michael
- highman@blink.sv
- Composer Artist | Musician
- 🎹🎼🎤🏸🏝️🐕❤️
- 在這裡可以看到「我看世界」的樣子
- 他是光良
- https://jumble.social/users/npub1kr5vqlelt8l47s2z0l47z4myqg897m04vrnaqks3emwryca3al7sv83ry3
-
 @ da8b7de1:c0164aee
2025-05-28 15:42:22
@ da8b7de1:c0164aee
2025-05-28 15:42:22Nemzetközi nukleáris energetikai hírek
Új amerikai kis moduláris reaktor engedélykérelem
A Tennessee Valley Authority (TVA) benyújtotta az Egyesült Államok Nukleáris Szabályozó Hatóságához (NRC) az engedélykérelmet egy GE Vernova Hitachi Nuclear Energy BWRX-300 kis moduláris reaktor (SMR) megépítésére a Clinch River telephelyen. Ez jelentős lépés az új, fejlett nukleáris technológiák bevezetésében az Egyesült Államokban, és jól mutatja, hogy az SMR-ek egyre fontosabb, rugalmas és skálázható tisztaenergia-megoldássá válnak[world-nuclear-news.org].
Amerikai elnöki rendeletek a nukleáris bővítés felgyorsítására
Donald Trump amerikai elnök négy elnöki rendeletet írt alá, amelyek célja a reaktorengedélyezési folyamatok gyorsítása, a hazai urántermelés növelése és a fejlett nukleáris technológiák bevezetésének felgyorsítása. Az új irányelvek ambiciózus célokat tűznek ki, például az amerikai nukleáris kapacitás megnégyszerezését 2050-re, az NRC számára az engedélyezési idő 18 hónapra csökkentését, valamint szövetségi területek kijelölését új nukleáris létesítmények számára. Ezeket a rendeleteket az „amerikai nukleáris reneszánsz” alapjának szánják, különös hangsúlyt fektetve az AI-ipar energiaigényeinek kielégítésére és a hazai gyártás újjáélesztésére[nucnet.org].
Iparági optimizmus és globális befektetési trendek
Az iparági vezetők egészséges és optimista kilátásokról számolnak be a nukleáris energia terén, kiemelve olyan aktív projekteket, mint a TerraPower Wyomingban, az X-energy és a Dow együttműködése, valamint a Westinghouse tevékenysége Lengyelországban. Különösen nagy az érdeklődés a magánbefektetések iránt a magas dúsítású, alacsony dúsítású urán (HALEU) előállítása terén, illetve annak lehetősége iránt, hogy a Világbank elkezdjen nukleáris projekteket finanszírozni, ami szélesebb körű nemzetközi befektetéseket is elindíthat[ans.org].
Nemzetközi fejlemények és ellátási lánc felkészültsége
Számos ország halad előre a nukleáris fejlesztésekkel: - Kína tíz új reaktort hagyott jóvá. - India szabályozó hatósága engedélyezte egy új, négyblokkos telephely létesítését Rádzsasztánban. - Belgium konzultációt indított egy innovatív, ólom-hűtésű kis moduláris reaktor terveiről. - Brazília várhatóan Oroszországgal közösen fejleszt SMR-projektet. - Csehország új nukleáris szerződéseket köt, a külső politikai nyomás ellenére is.
A globális nukleáris ellátási láncot arra ösztönzik, hogy készüljön fel a gyors növekedésre, kiemelve a helyi és nemzetközi együttműködés fontosságát a növekvő igények kielégítésére[world-nuclear-news.org].
Úszó atomerőművek és tengeri innovációk
Az úszó atomerőművek továbbra is az innováció középpontjában állnak: - Oroszország Akademik Lomonosov nevű úszó atomerőműve elérte az első milliárd kilowattóra termelést. - Az Egyesült Királyságban a Core Power egy amerikai központú tengeri nukleáris programot fejleszt, melynek célja úszó reaktorok telepítése amerikai kikötőkben a 2030-as évek közepére. - A dán Seaborg Technologies (új nevén Saltfoss Energy) kompakt olvadt só reaktor technológián dolgozik, amelyet szintén a 2030-as évekre terveznek bevezetni. - A Westinghouse és a Core Power együttműködik egy úszó atomerőmű fejlesztésén az eVinci mikroreaktorral[world-nuclear-news.org].
Érintettek bevonása és társadalmi bizalom
A Nemzetközi Atomenergia-ügynökség (IAEA) kiemeli az érintettek bevonásának fontosságát a nukleáris energia jövője szempontjából. Folyamatban lévő konferenciáján olyan témákat tárgyalnak, mint a nukleáris energia szerepe az ipari dekarbonizációban, a nyilvános meghallgatások értéke a projektek átláthatósága érdekében, valamint a társadalmi bizalom és a szabályozói megfelelés legjobb gyakorlatai, különösen az új technológiák, például az SMR-ek bevezetése során[iaea.org].
Források: - world-nuclear-news.org - nucnet.org - iaea.org - ans.org
-
 @ 33baa074:3bb3a297
2025-05-28 08:54:40
@ 33baa074:3bb3a297
2025-05-28 08:54:40COD (chemical oxygen demand) sensors play a vital role in water quality testing. Their main functions include real-time monitoring, pollution event warning, water quality assessment and pollution source tracking. The following are the specific roles and applications of COD sensors in water quality testing:
Real-time monitoring and data acquisition COD sensors can monitor the COD content in water bodies in real time and continuously. Compared with traditional sampling methods, COD sensors are fast and accurate, without manual sampling and laboratory testing, which greatly saves time and labor costs. By combining with the data acquisition system, the monitoring data can be uploaded to the cloud in real time to form a extemporization distribution map of the COD content in the water body, providing detailed data support for environmental monitoring and management.
Pollution event warning and rapid response COD sensors play an important role in early warning and rapid response in water environment monitoring. Once there is an abnormal increase in organic matter in the water body, the COD sensor can quickly detect the change in COD content and alarm through the preset threshold. This enables relevant departments to take measures at the early stage of the pollution incident to prevent the spread of pollution and protect the water environment.
Water quality assessment and pollution source tracking COD sensors play an important role in water quality assessment and pollution source tracking. By continuously monitoring the COD content in water bodies, the water quality can be evaluated and compared with national and regional water quality standards. At the same time, COD sensors can also help determine and track the location and spread of pollution sources, provide accurate data support for environmental management departments, and guide the development of pollution prevention and control work.
Application scenarios COD sensors are widely used in various water quality monitoring scenarios, including but not limited to: Sewage treatment plants: used to monitor the COD content of in fluent and effluent to ensure the effect of sewage treatment. Water source protection and management: deployed in water sources to monitor the COD content of in fluent sources. Once the water quality exceeds the set limit, the system will issue an alarm in time to ensure water quality safety. Lake and river monitoring: deployed in water bodies such as lakes and rivers to monitor the COD content of water bodies in real time.

Technical features of COD sensor COD sensor uses advanced technology, such as ultraviolet absorption method, which does not require the use of chemical reagents, avoiding the risk of contamination of chemical reagents in traditional COD detection methods, and can achieve online uninterrupted water quality monitoring, providing strong support for real-time water quality assessment. In addition, COD sensor also has the advantages of low cost, high stability, strong anti-interference ability, and convenient installation.
Summary In summary, COD sensor plays an irreplaceable role in water quality detection. It can not only provide real-time and accurate water quality data, but also quickly warn when pollution incidents occur, providing strong technical support for water quality management and environmental protection. With the advancement of technology and the popularization of applications, COD sensor will play a more important role in water quality monitoring in the future.
-
 @ 866e0139:6a9334e5
2025-05-23 17:57:24
@ 866e0139:6a9334e5
2025-05-23 17:57:24Autor: Caitlin Johnstone. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Ich hörte einem jungen Autor zu, der eine Idee beschrieb, die ihn so sehr begeisterte, dass er die Nacht zuvor nicht schlafen konnte. Und ich erinnerte mich daran, wie ich mich früher – vor Gaza – über das Schreiben freuen konnte. Dieses Gefühl habe ich seit 2023 nicht mehr gespürt.
Ich beklage mich nicht und bemitleide mich auch nicht selbst, ich stelle einfach fest, wie unglaublich düster und finster die Welt in dieser schrecklichen Zeit geworden ist. Es wäre seltsam und ungesund, wenn ich in den letzten anderthalb Jahren Freude an meiner Arbeit gehabt hätte. Diese Dinge sollen sich nicht gut anfühlen. Nicht, wenn man wirklich hinschaut und ehrlich zu sich selbst ist in dem, was man sieht.
Es war die ganze Zeit über so hässlich und so verstörend. Es gibt eigentlich keinen Weg, all diesen Horror umzudeuten oder irgendwie erträglich zu machen. Alles, was man tun kann, ist, an sich selbst zu arbeiten, um genug inneren Raum zu schaffen, um die schlechten Gefühle zuzulassen und sie ganz durchzufühlen, bis sie sich ausgedrückt haben. Lass die Verzweiflung herein. Die Trauer. Die Wut. Den Schmerz. Lass sie deinen Körper vollständig durchfließen, ohne Widerstand, und steh dann auf und schreibe das nächste Stück.
Das ist es, was Schreiben für mich jetzt ist. Es ist nie etwas, worüber ich mich freue, es zu teilen, oder wofür ich von Inspiration erfüllt bin. Wenn überhaupt, dann fühlt es sich eher so an wie: „Okay, hier bitte, es tut mir schrecklich leid, dass ich euch das zeigen muss, Leute.“ Es ist das Starren in die Dunkelheit, in das Blut, in das Gemetzel, in die gequälten Gesichter – und das Aufschreiben dessen, was ich sehe, Tag für Tag.
Nichts daran ist angenehm oder befriedigend. Es ist einfach das, was man tut, wenn ein Genozid in Echtzeit vor den eigenen Augen stattfindet, mit der Unterstützung der eigenen Gesellschaft. Alles daran ist entsetzlich, und es gibt keinen Weg, das schönzureden – aber man tut, was getan werden muss. So, wie man es täte, wenn es die eigene Familie wäre, die da draußen im Schutt liegt.
Dieser Genozid hat mich für immer verändert. Er hat viele Menschen für immer verändert. Wir werden nie wieder dieselben sein. Die Welt wird nie wieder dieselbe sein. Ganz gleich, was passiert oder wie dieser Albtraum endet – die Dinge werden nie wieder so sein wie zuvor.
Und das sollten sie auch nicht. Der Holocaust von Gaza ist das Ergebnis der Welt, wie sie vor ihm war. Unsere Gesellschaft hat ihn hervorgebracht – und jetzt starrt er uns allen direkt ins Gesicht. Das sind wir. Das ist die Frucht des Baumes, den die westliche Zivilisation bis zu diesem Punkt gepflegt hat.
Jetzt geht es nur noch darum, alles zu tun, was wir können, um den Genozid zu beenden – und sicherzustellen, dass die Welt die richtigen Lehren daraus zieht. Das ist eines der würdigsten Anliegen, denen man sich in diesem Leben widmen kann.
Ich habe noch immer Hoffnung, dass wir eine gesunde Welt haben können. Ich habe noch immer Hoffnung, dass das Schreiben über das, was geschieht, eines Tages wieder Freude bereiten kann. Aber diese Dinge liegen auf der anderen Seite eines langen, schmerzhaften, konfrontierenden Weges, der in den kommenden Jahren vor uns liegt. Es gibt keinen Weg daran vorbei.
Die Welt kann keinen Frieden und kein Glück finden, solange wir uns nicht vollständig damit auseinandergesetzt haben, was wir Gaza angetan haben.
Dieser Text ist die deutsche Übersetzung dieses Substack-Artikels von Caitlin Johnstone.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 4d41a7cb:7d3633cc
2025-04-08 01:17:39
@ 4d41a7cb:7d3633cc
2025-04-08 01:17:39Satoshi Nakamoto, the pseudonymous creator of Bitcoin, registered his birthday as April 5, 1975, on his P2P Foundation profile. Many think that he chose this date because on that same day in 1933, the United States government confiscated the gold of the American people. Whether this was on purpose or not, what happened in this day is very important to understand how do we ended up here.
In 1933, as expressed in Roosevelt’s Executive Orders 6073, 6102, and 6260, the United States first declared bankruptcy. The bankrupt U.S. went into receivership in 1933. America was turned over via receivership and reorganization in favor of its creditors. These creditors, the International Bankers, from the beginning stated their intent, which was to plunder, bankrupt, conquer and enslave America and return it to its colonial status.1
As one of his first acts as President, Franklin Delano Roosevelt declared a “Banking Emergency” to bail out the Federal Reserve Bank, which had embezzled this country’s gold supply. The Congress gave the President dictatorial powers under the “War Powers Act of 1917” (amended 1933), written, by the way, by the Board of Governors of the Federal Reserve Bank of New York.2
This day marked the official abandonment of the American Constitution, law and real money. Today, 92 years after this event, most of the people living today have never had any real money or paid for anything using real money; unless they used Bitcoin...
There could be no bankruptcy if there was not a private central bank lending paper currency to the government at interest, so we must start from 1913, when the Federal Reserve was created: a non-federal private bank with no reserves and the monopoly of issuing debt based paper currency in unlimited amounts and lending it to the government at interest by buying treasury bills. The fact that this currency is lent into existence at interest makes the debt mathematically impossible to be repaid; it can only be refinanced or defaulted.
Between 1929 and 1933, the Federal Reserve Bank reduced the currency supply by 33%, thereby creating the Great Depression, bankrupting the US government, stealing the Americans’ gold supply, and officially ending the gold standard. Since then the US dollar (money) was replaced with Federal Reserve Notes (debt). This was also the end of the Republican form of government and the beginning of a socialist mob rule democracy (Fascism).
“Fascism should more properly be called corporatism because it is the merger of state and corporate power.” — Benito Mussolini
The United States government has been bankrupt since 1933, since it defaulted on its gold bonds. This type of bond existed until 1933, when the U.S. monetary system abandoned the gold standard. 3 From this year the government has been totally controlled by the International bankers and used as a tool to spread and maintain their power worldwide.
Many people think that the gold standard was abandoned in 1971, but this is not true; in fact, this happened in 1933 when the US dollar was replaced by Federal Reserve Notes that are 100% debt-based fiat paper currency.
The year 1933 in the United States marked:
- The end of the Republican form of government and the beginning of American Fascism
- The end of the United States dollar and its replacement by Federal Reserve Notes
- The abandonment of common law and replacement with military admiralty law
- The takeover of the United States government by International bankers
- A massive gold theft and the end of the US gold standard
- The exchange of rights with privileges and licenses
- The United States government bankruptcy
The next shameful event in our history which still plagues us to this day was the “War Powers Act of 1933.” This Act permitted President Roosevelt to make law in the form of Executive Order, bypass Congress and create his socialist state. We (citizens of this country) were ever after to be considered enemies of the United States who must be licensed to engage in any commercial activity. With the aid of the Federal Reserve (the same people who created the Depression), the President confiscated our gold and silver coin and replaced it with worthless pieces of paper and a debt system that will eventually destroy this great country. Our land and our labor were pledged to the Federal Reserve Bank, Inc., as collateral for a debt system that could never be paid.4
“Emergency Powers” means any form of military style government, martial law, or martial rule. Martial law and martial rule are not the same.
United States Congressional Record March 17, 1993 Vol. #33, page H- 1303, Congressman James Traficant, Jr. (Ohio) addressing the House:
“Mr. Speaker, we are here now in chapter 11. Members of Congress are official trustees presiding over the greatest reorganization of any Bankrupt entity in world history, the U.S. Government. We are setting forth, hopefully, a blueprint for our future”
“There are some who say it is a coroner’s report that will lead to our demise. It is an established fact that the United States Federal Government has been dissolved by the Emergency Banking Act, March 9, 1933, 48 Stat. 1, Public Law 89-719; dered by President Roosevelt, being bankrupt and insolvent. H.J.R. 192, 73rd Congress in session June 5, 1933 – Joint Resolution To Suspend The Gold Standard and Abrogate the Gold Clause dissolved the Sovereign Authority of the United States and the official capacities of all United States Governmental Offices, Officers, and Departments and is further evidence that the United States Federal Government exists today in name only” **“The receivers of the United States Bankruptcy are the International Bankers, via the United Nations, the World Bank and the International Monetary Fund”
“All United States Offices, Officials, and Departments are now operating within a de facto status in name only under Emergency War Powers. With the Constitutional Republican form of Government now dissolved, the receivers of the Bankruptcy have adopted a new form of government for the United States. This new form of government is known as a Democracy, being an established Socialist/Communist order under a new governor for America. This act was instituted and established by transferring and/or placing the Office of the Secretary of Treasury to that of the Governor of the International Monetary Fund. Public Law 94-564, page 8, Section H.R. 13955 read in part:”
“The U.S. Secretary of Treasury receives no compensation for representing the United States.”
The American Spirit
The intention of the founding fathers of the United States was to create a constitutional republic to protect natural human rights and escape from the tyrannical English monarchy and its usurious Bank of England's monetary system. They created an honest monetary system based on gold and silver (United State Dollar) and got rid of nobility titles, creating equality under the law.
Section 10 of the American Constitution says:
No State shall enter into any Treaty, Alliance, or Confederation; grant Letters of Marque and Reprisal; coin Money; emit Bills of Credit; make anything but gold and silver Coin a tender in payment of debts; pass any bill of attainder, ex post facto law, or law impairing the obligation of contracts; or grant any title of nobility.
The United States Dollar (1792-1933)
A dollar is a measure of weight defined by the Coinage Act of 1792 and 1900, which specifies a certain quantity—24.8 grains of gold or 371.25 grains of silver (from 1792 to 1900) when the American dollar was based on a bimetallic standard.
The Gold Standard Act of 1900 formally placed the United States on the gold standard, setting the value of one dollar at 25.8 grams of 90% pure gold, which fixed the price of gold at $20.67 per troy ounce. This standard was totally abandoned in 1933.
Gold and silver were such powerful money during the founding of the United States of America that the founding fathers declared that only gold or silver coins could be “money” in America.
But since the greedy bankers cannot profit from honest money they cannot print, they replaced the money with paper debt instruments. And by doing this, they have effectively enslaved the American people until today. My definition of modern slavery is working for a currency that someone else can create at no cost or effort. What's worse is that they even demand to be paid back and with interest!
Federal Reserve Notes (1913-present)
Federal Reserve Notes are not real money. Money that has metallic or other intrinsic value, as distinguished from paper currency, checks, and drafts.
Federal Reserve Notes (FRNs) are a legal fiction. An assumption that something is true even though it may be untrue. 5 The assumption that they are money, when in fact they are the opposite of money: debt or paper currency.
Paper money. Paper documents that circulate as currency; bills drawn by a government against its own credit. 6 Like Goldsmiths' notes. Hist. Bankers' cash notes: promissory notes given by bankers to customers as acknowledgments of the receipt of money. • This term derives from the London banking business, which originally was transacted by goldsmiths.7
These notes were scientifically designed to bankrupt the government and slave the American people, as Alfred Owen Crozier warned one year before the bill for the creation of the FED was passed through Congress (1912):
If Congress yields and authorizes a private central bank as proposed by the pending bill, the end when the bubble bursts will be universal ruin and national bankruptcy.
Unfortunately, the bill was passed in 1913, and this private bank started printing a new currency different from the US dollar creating the great depression and effectible bankrupting the government like Alfred warned 20 years before.
Alfred also warned:
Thus the way is opened for an unlimited inflation of corporate paper currency issued by a mere private corporation with relatively small net assets and no government guarantee, every dollar supposed to be redeemable in gold, but with not a single dollar of gold necessarily held in the reserves of such corporation to accomplish such redemption.
Differently from what's commonly believed Federal Reserve Notes (FRNs) were never really “backed” by gold; they were never supposed to be hard currency. Currency backed by reserves, esp. gold and silver reserves.
The United States government defaulted on its gold clauses, calling for payment in gold. This marked the end of the gold standard. A monetary system in which currency is convertible into its legal equivalent in gold or gold coin.
Since then we have been under a paper standard, where we use fake money as tender for payments. Paper standard. A monetary system based entirely on paper; a system of currency that is not convertible into gold or other precious metal.
People traded their coupons as money or “currency.” Currency is not money but a money substitute. Redeemable currency must promise to pay a dollar equivalent in gold or silver money. Federal Reserve Notes (FRNs) make no such promises and are not “money.” A Federal Reserve Note is a debt obligation of the federal United States government, not “money.” The federal United States government and the U.S. Congress were not and have never been authorized by the Constitution of the United States of America to issue currency of any kind, but only lawful money—gold and silver coin.8
A bona fide note can be used in a financial transaction to discharge the debt only because it is an unconditional promise to pay by the issuer to the bearer. Is a Federal Reserve Note a contract note, an unconditional promise to pay? At one time the Federal Reserve issued bona fide contractual notes and certificates, redeemable in gold and silver coin. Most people never saw or comprehended the contract. It went largely unread because the Federal Reserve very cunningly hid the contract on the face of the note by breaking it up into five separate lines of text with a significantly different typeface for each line and placing the president’s picture right in the middle of it. They even used the old attorney’s ruse of obscuring the most important text in fine print! Over time, the terms and conditions of the contract were diluted until eventually they literally became an I.O.U. for nothing.
FEDERAL RESERVE NOTE
-
THIS NOTE IS LEGAL TENDER FOR ALL DEBT, PUBLIC AND PRIVATE, AND IT IS REDEEMABLE IN LAWFUL MONEY AT THE UNITED STATES TREASURY OR ANY FEDERAL RESERVE BANK.
-
DATE: SERIES OF 1934
-
WILL PAY TO THE BEARER ON DEMAND: ONE HUNDRED DOLLARS
-
TREASURER OF THE UNITED STATES SIGNATURE
-
SECRETARY OF THE TREASURY SIGNATURE

Nowadays FRNs say "This note is legal tender for all debts public and private" it tender debt but it does not pay the bearer on demand. It value was stolen by a counterfeiting technique commonly know as inflation.
One hundred dollars (SERIES OF 1934) will be 2480 grains of gold, or 159.4 grams, or 5.1249 troy ounces. Today one troy ounce is priced around $3,000 federal reserve notes. 5.1249 X 3,000 = $15,375 actual FRNs.
A $100 FRN bill today will buy 0.65% of a real gold $100 dollar certificate. That’s a -99.35% loss of purchasing power in the last 91 years.
FRNs savers have been rugged pulled!
Gold bugs where the winners...
But Bitcoin is even better...
Happy birthday Satoshi! April 5 will be forever remembered.
Satoshi... The man, the myth, the Legend...
-
 @ 866e0139:6a9334e5
2025-05-22 06:51:15
@ 866e0139:6a9334e5
2025-05-22 06:51:15Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
https://www.youtube.com/watch?v=gjndTXyk3mw
Im Jahr 1954, als Frankreich gerade dabei war, seine kolonialen Kriege in Indochina und Algerien zu verschärfen, schrieb Boris Vian ein Lied – oder vielmehr: einen poetischen Faustschlag. Le Déserteur ist keine Ballade, sondern ein Manifest. Keine Hymne auf den Frieden, sondern eine Anklage gegen den Krieg. Adressiert an den Präsidenten, beginnt das Chanson wie ein höflicher Brief – und endet als flammender Akt des zivilen Ungehorsams.
„Herr Präsident,\ ich schreibe Ihnen einen Brief,\ den Sie vielleicht lesen werden,\ wenn Sie Zeit haben.“
Was folgt, ist ein klassischer Kriegsdienstverweigerungsbrief, aber eben kein bürokratischer. Vian spricht nicht in Paragraphen, sondern in Herzschlägen. Der Erzähler, ein einfacher Mann, will nicht kämpfen. Nicht für irgendein Vaterland, nicht für irgendeine Fahne, nicht für irgendeinen ideologischen Zweck.
„Ich soll zur Welt gekommen sein,\ um zu leben, nicht um zu sterben.“
70 Jahre später klingt diese Zeile wie ein Skandal. In einer Zeit, in der die Ukraine junge Männer für Kopfgeld auf der Straße zwangsrekrutiert und in Stahlgewitter schickt, in der palästinensische Jugendliche im Gazastreifen unter Trümmern begraben werden, während israelische Reservisten mit Dauerbefehl marschieren – ist Le Déserteur ein sakraler Text geworden. Fast ein Gebet.
„Wenn man mich verfolgt,\ werde ich den Gehorsam verweigern.\ Ich werde keine Waffe in die Hand nehmen,\ ich werde fliehen, bis ich Frieden finde.“
Wie viele „Deserteure“ gibt es heute, die wir gar nicht kennen? Menschen, die sich nicht auf die Seite der Bomben stellen wollen – egal, wer sie wirft? Die sich nicht mehr einspannen lassen zwischen Propaganda und Patriotismus? Die ihre Menschlichkeit über jeden nationalen Befehl stellen?
Der Krieg, sagt Vian, macht aus freien Menschen Befehlsempfänger und aus Söhnen Leichen. Und wer heute sagt, es gebe „gerechte Kriege“, sollte eine Frage beantworten: Ist es auch ein gerechter Tod?
Darum: Verweigert.
Verweigert den Befehl, zu hassen.\ Verweigert den Reflex, Partei zu ergreifen.\ Verweigert den Dienst an der Waffe.
Denn wie Vian singt:
„Sagen Sie's den Leuten:\ Ich werde nicht kommen.“
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ ec9bd746:df11a9d0
2025-04-06 08:06:08
@ ec9bd746:df11a9d0
2025-04-06 08:06:08🌍 Time Window:
🕘 When: Every even week on Sunday at 9:00 PM CET
🗺️ Where: https://cornychat.com/eurocornStart: 21:00 CET (Prague, UTC+1)
End: approx. 02:00 CET (Prague, UTC+1, next day)
Duration: usually 5+ hours.| Region | Local Time Window | Convenience Level | |-----------------------------------------------------|--------------------------------------------|---------------------------------------------------------| | Europe (CET, Prague) 🇨🇿🇩🇪 | 21:00–02:00 CET | ✅ Very Good; evening & night | | East Coast North America (EST) 🇺🇸🇨🇦 | 15:00–20:00 EST | ✅ Very Good; afternoon & early evening | | West Coast North America (PST) 🇺🇸🇨🇦 | 12:00–17:00 PST | ✅ Very Good; midday & afternoon | | Central America (CST) 🇲🇽🇨🇷🇬🇹 | 14:00–19:00 CST | ✅ Very Good; afternoon & evening | | South America West (Peru/Colombia PET/COT) 🇵🇪🇨🇴 | 15:00–20:00 PET/COT | ✅ Very Good; afternoon & evening | | South America East (Brazil/Argentina/Chile, BRT/ART/CLST) 🇧🇷🇦🇷🇨🇱 | 17:00–22:00 BRT/ART/CLST | ✅ Very Good; early evening | | United Kingdom/Ireland (GMT) 🇬🇧🇮🇪 | 20:00–01:00 GMT | ✅ Very Good; evening hours (midnight convenient) | | Eastern Europe (EET) 🇷🇴🇬🇷🇺🇦 | 22:00–03:00 EET | ✅ Good; late evening & early night (slightly late) | | Africa (South Africa, SAST) 🇿🇦 | 22:00–03:00 SAST | ✅ Good; late evening & overnight (late-night common) | | New Zealand (NZDT) 🇳🇿 | 09:00–14:00 NZDT (next day) | ✅ Good; weekday morning & afternoon | | Australia (AEDT, Sydney) 🇦🇺 | 07:00–12:00 AEDT (next day) | ✅ Good; weekday morning to noon | | East Africa (Kenya, EAT) 🇰🇪 | 23:00–04:00 EAT | ⚠️ Slightly late (night hours; late night common) | | Russia (Moscow, MSK) 🇷🇺 | 23:00–04:00 MSK | ⚠️ Slightly late (join at start is fine, very late night) | | Middle East (UAE, GST) 🇦🇪🇴🇲 | 00:00–05:00 GST (next day) | ⚠️ Late night start (midnight & early morning, but shorter attendance plausible)| | Japan/Korea (JST/KST) 🇯🇵🇰🇷 | 05:00–10:00 JST/KST (next day) | ⚠️ Early; convenient joining from ~07:00 onwards possible | | China (Beijing, CST) 🇨🇳 | 04:00–09:00 CST (next day) | ❌ Challenging; very early morning start (better ~07:00 onwards) | | India (IST) 🇮🇳 | 01:30–06:30 IST (next day) | ❌ Very challenging; overnight timing typically difficult|
-
 @ 6e0ea5d6:0327f353
2025-05-28 04:34:08
@ 6e0ea5d6:0327f353
2025-05-28 04:34:08Ascolta bene! It is more dignified to thirst alone in the desert than to share wine with someone who has no thirst for conquest.
On the silent path to success, it’s not the declared enemies who slow the march, but rather the friends. Not the noble or loyal ones, but the failures—those who carry a dull glint in their eyes, chronic laziness in their spirit, and the eternal excuse of bad luck in their pockets. Friendship, when poorly chosen, becomes a polished anchor, tied to your ankle with ropes named camaraderie.
Nothing weighs heavier on the journey than having to endure the failed and envious around you. It is a kind of emotional parasitism that begins with empathy and ends in stagnation. Those who live among the weak will crawl. Those who keep company with miserable friends, instead of striving to prosper, learn to curse wealth—not out of ethics, but out of envy. Mediocrity, my friend, is contagious. And it does not take root suddenly, but like a silent epidemic.
Ambition—that fire that burns in the bones of great men—will always seem like arrogance to the ears of the failed. Those who have never built anything, except arguments to justify their paralysis, will never understand the fury of someone born to conquer. And so, with smiles, they spit venom: “Calm down,” they say, “be content,” they advise. Hypocrites. What they call humility is nothing more than resignation to their own defeat.
To walk alone, with hunger and honor, is worth more than feasting at lavish tables at the cost of your own sweat, surrounded by parasites who toast your downfall with glasses full of praise. No one prospers where the conversation is filled with complaints, criticism, and envy. What does not build up, corrodes.
The rust of the weak is invisible at first—a bitter joke here, a veiled critique there. And before you know it, the structure is already rotten. Of the friendship, only the weight remains. Of the relationship, only exhaustion. The true enemy of success is the company of those who have failed and wish for you the same fate. These tragic figures—always tired, always victims—are masters of collective self-sabotage.
Feel no remorse in abandoning those who build nothing and consume everything. And in that abandonment, you become freer, stronger, and unbreakable.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ 6f6b50bb:a848e5a1
2024-12-15 15:09:52
@ 6f6b50bb:a848e5a1
2024-12-15 15:09:52Che cosa significherebbe trattare l'IA come uno strumento invece che come una persona?
Dall’avvio di ChatGPT, le esplorazioni in due direzioni hanno preso velocità.
La prima direzione riguarda le capacità tecniche. Quanto grande possiamo addestrare un modello? Quanto bene può rispondere alle domande del SAT? Con quanta efficienza possiamo distribuirlo?
La seconda direzione riguarda il design dell’interazione. Come comunichiamo con un modello? Come possiamo usarlo per un lavoro utile? Quale metafora usiamo per ragionare su di esso?
La prima direzione è ampiamente seguita e enormemente finanziata, e per una buona ragione: i progressi nelle capacità tecniche sono alla base di ogni possibile applicazione. Ma la seconda è altrettanto cruciale per il campo e ha enormi incognite. Siamo solo a pochi anni dall’inizio dell’era dei grandi modelli. Quali sono le probabilità che abbiamo già capito i modi migliori per usarli?
Propongo una nuova modalità di interazione, in cui i modelli svolgano il ruolo di applicazioni informatiche (ad esempio app per telefoni): fornendo un’interfaccia grafica, interpretando gli input degli utenti e aggiornando il loro stato. In questa modalità, invece di essere un “agente” che utilizza un computer per conto dell’essere umano, l’IA può fornire un ambiente informatico più ricco e potente che possiamo utilizzare.
Metafore per l’interazione
Al centro di un’interazione c’è una metafora che guida le aspettative di un utente su un sistema. I primi giorni dell’informatica hanno preso metafore come “scrivanie”, “macchine da scrivere”, “fogli di calcolo” e “lettere” e le hanno trasformate in equivalenti digitali, permettendo all’utente di ragionare sul loro comportamento. Puoi lasciare qualcosa sulla tua scrivania e tornare a prenderlo; hai bisogno di un indirizzo per inviare una lettera. Man mano che abbiamo sviluppato una conoscenza culturale di questi dispositivi, la necessità di queste particolari metafore è scomparsa, e con esse i design di interfaccia skeumorfici che le rafforzavano. Come un cestino o una matita, un computer è ora una metafora di se stesso.
La metafora dominante per i grandi modelli oggi è modello-come-persona. Questa è una metafora efficace perché le persone hanno capacità estese che conosciamo intuitivamente. Implica che possiamo avere una conversazione con un modello e porgli domande; che il modello possa collaborare con noi su un documento o un pezzo di codice; che possiamo assegnargli un compito da svolgere da solo e che tornerà quando sarà finito.
Tuttavia, trattare un modello come una persona limita profondamente il nostro modo di pensare all’interazione con esso. Le interazioni umane sono intrinsecamente lente e lineari, limitate dalla larghezza di banda e dalla natura a turni della comunicazione verbale. Come abbiamo tutti sperimentato, comunicare idee complesse in una conversazione è difficile e dispersivo. Quando vogliamo precisione, ci rivolgiamo invece a strumenti, utilizzando manipolazioni dirette e interfacce visive ad alta larghezza di banda per creare diagrammi, scrivere codice e progettare modelli CAD. Poiché concepiamo i modelli come persone, li utilizziamo attraverso conversazioni lente, anche se sono perfettamente in grado di accettare input diretti e rapidi e di produrre risultati visivi. Le metafore che utilizziamo limitano le esperienze che costruiamo, e la metafora modello-come-persona ci impedisce di esplorare il pieno potenziale dei grandi modelli.
Per molti casi d’uso, e specialmente per il lavoro produttivo, credo che il futuro risieda in un’altra metafora: modello-come-computer.
Usare un’IA come un computer
Sotto la metafora modello-come-computer, interagiremo con i grandi modelli seguendo le intuizioni che abbiamo sulle applicazioni informatiche (sia su desktop, tablet o telefono). Nota che ciò non significa che il modello sarà un’app tradizionale più di quanto il desktop di Windows fosse una scrivania letterale. “Applicazione informatica” sarà un modo per un modello di rappresentarsi a noi. Invece di agire come una persona, il modello agirà come un computer.
Agire come un computer significa produrre un’interfaccia grafica. Al posto del flusso lineare di testo in stile telescrivente fornito da ChatGPT, un sistema modello-come-computer genererà qualcosa che somiglia all’interfaccia di un’applicazione moderna: pulsanti, cursori, schede, immagini, grafici e tutto il resto. Questo affronta limitazioni chiave dell’interfaccia di chat standard modello-come-persona:
-
Scoperta. Un buon strumento suggerisce i suoi usi. Quando l’unica interfaccia è una casella di testo vuota, spetta all’utente capire cosa fare e comprendere i limiti del sistema. La barra laterale Modifica in Lightroom è un ottimo modo per imparare l’editing fotografico perché non si limita a dirti cosa può fare questa applicazione con una foto, ma cosa potresti voler fare. Allo stesso modo, un’interfaccia modello-come-computer per DALL-E potrebbe mostrare nuove possibilità per le tue generazioni di immagini.
-
Efficienza. La manipolazione diretta è più rapida che scrivere una richiesta a parole. Per continuare l’esempio di Lightroom, sarebbe impensabile modificare una foto dicendo a una persona quali cursori spostare e di quanto. Ci vorrebbe un giorno intero per chiedere un’esposizione leggermente più bassa e una vibranza leggermente più alta, solo per vedere come apparirebbe. Nella metafora modello-come-computer, il modello può creare strumenti che ti permettono di comunicare ciò che vuoi più efficientemente e quindi di fare le cose più rapidamente.
A differenza di un’app tradizionale, questa interfaccia grafica è generata dal modello su richiesta. Questo significa che ogni parte dell’interfaccia che vedi è rilevante per ciò che stai facendo in quel momento, inclusi i contenuti specifici del tuo lavoro. Significa anche che, se desideri un’interfaccia più ampia o diversa, puoi semplicemente richiederla. Potresti chiedere a DALL-E di produrre alcuni preset modificabili per le sue impostazioni ispirati da famosi artisti di schizzi. Quando clicchi sul preset Leonardo da Vinci, imposta i cursori per disegni prospettici altamente dettagliati in inchiostro nero. Se clicchi su Charles Schulz, seleziona fumetti tecnicolor 2D a basso dettaglio.
Una bicicletta della mente proteiforme
La metafora modello-come-persona ha una curiosa tendenza a creare distanza tra l’utente e il modello, rispecchiando il divario di comunicazione tra due persone che può essere ridotto ma mai completamente colmato. A causa della difficoltà e del costo di comunicare a parole, le persone tendono a suddividere i compiti tra loro in blocchi grandi e il più indipendenti possibile. Le interfacce modello-come-persona seguono questo schema: non vale la pena dire a un modello di aggiungere un return statement alla tua funzione quando è più veloce scriverlo da solo. Con il sovraccarico della comunicazione, i sistemi modello-come-persona sono più utili quando possono fare un intero blocco di lavoro da soli. Fanno le cose per te.
Questo contrasta con il modo in cui interagiamo con i computer o altri strumenti. Gli strumenti producono feedback visivi in tempo reale e sono controllati attraverso manipolazioni dirette. Hanno un overhead comunicativo così basso che non è necessario specificare un blocco di lavoro indipendente. Ha più senso mantenere l’umano nel loop e dirigere lo strumento momento per momento. Come stivali delle sette leghe, gli strumenti ti permettono di andare più lontano a ogni passo, ma sei ancora tu a fare il lavoro. Ti permettono di fare le cose più velocemente.
Considera il compito di costruire un sito web usando un grande modello. Con le interfacce di oggi, potresti trattare il modello come un appaltatore o un collaboratore. Cercheresti di scrivere a parole il più possibile su come vuoi che il sito appaia, cosa vuoi che dica e quali funzionalità vuoi che abbia. Il modello genererebbe una prima bozza, tu la eseguirai e poi fornirai un feedback. “Fai il logo un po’ più grande”, diresti, e “centra quella prima immagine principale”, e “deve esserci un pulsante di login nell’intestazione”. Per ottenere esattamente ciò che vuoi, invierai una lista molto lunga di richieste sempre più minuziose.
Un’interazione alternativa modello-come-computer sarebbe diversa: invece di costruire il sito web, il modello genererebbe un’interfaccia per te per costruirlo, dove ogni input dell’utente a quell’interfaccia interroga il grande modello sotto il cofano. Forse quando descrivi le tue necessità creerebbe un’interfaccia con una barra laterale e una finestra di anteprima. All’inizio la barra laterale contiene solo alcuni schizzi di layout che puoi scegliere come punto di partenza. Puoi cliccare su ciascuno di essi, e il modello scrive l’HTML per una pagina web usando quel layout e lo visualizza nella finestra di anteprima. Ora che hai una pagina su cui lavorare, la barra laterale guadagna opzioni aggiuntive che influenzano la pagina globalmente, come accoppiamenti di font e schemi di colore. L’anteprima funge da editor WYSIWYG, permettendoti di afferrare elementi e spostarli, modificarne i contenuti, ecc. A supportare tutto ciò è il modello, che vede queste azioni dell’utente e riscrive la pagina per corrispondere ai cambiamenti effettuati. Poiché il modello può generare un’interfaccia per aiutare te e lui a comunicare più efficientemente, puoi esercitare più controllo sul prodotto finale in meno tempo.
La metafora modello-come-computer ci incoraggia a pensare al modello come a uno strumento con cui interagire in tempo reale piuttosto che a un collaboratore a cui assegnare compiti. Invece di sostituire un tirocinante o un tutor, può essere una sorta di bicicletta proteiforme per la mente, una che è sempre costruita su misura esattamente per te e il terreno che intendi attraversare.
Un nuovo paradigma per l’informatica?
I modelli che possono generare interfacce su richiesta sono una frontiera completamente nuova nell’informatica. Potrebbero essere un paradigma del tutto nuovo, con il modo in cui cortocircuitano il modello di applicazione esistente. Dare agli utenti finali il potere di creare e modificare app al volo cambia fondamentalmente il modo in cui interagiamo con i computer. Al posto di una singola applicazione statica costruita da uno sviluppatore, un modello genererà un’applicazione su misura per l’utente e le sue esigenze immediate. Al posto della logica aziendale implementata nel codice, il modello interpreterà gli input dell’utente e aggiornerà l’interfaccia utente. È persino possibile che questo tipo di interfaccia generativa sostituisca completamente il sistema operativo, generando e gestendo interfacce e finestre al volo secondo necessità.
All’inizio, l’interfaccia generativa sarà un giocattolo, utile solo per l’esplorazione creativa e poche altre applicazioni di nicchia. Dopotutto, nessuno vorrebbe un’app di posta elettronica che occasionalmente invia email al tuo ex e mente sulla tua casella di posta. Ma gradualmente i modelli miglioreranno. Anche mentre si spingeranno ulteriormente nello spazio di esperienze completamente nuove, diventeranno lentamente abbastanza affidabili da essere utilizzati per un lavoro reale.
Piccoli pezzi di questo futuro esistono già. Anni fa Jonas Degrave ha dimostrato che ChatGPT poteva fare una buona simulazione di una riga di comando Linux. Allo stesso modo, websim.ai utilizza un LLM per generare siti web su richiesta mentre li navighi. Oasis, GameNGen e DIAMOND addestrano modelli video condizionati sull’azione su singoli videogiochi, permettendoti di giocare ad esempio a Doom dentro un grande modello. E Genie 2 genera videogiochi giocabili da prompt testuali. L’interfaccia generativa potrebbe ancora sembrare un’idea folle, ma non è così folle.
Ci sono enormi domande aperte su come apparirà tutto questo. Dove sarà inizialmente utile l’interfaccia generativa? Come condivideremo e distribuiremo le esperienze che creiamo collaborando con il modello, se esistono solo come contesto di un grande modello? Vorremmo davvero farlo? Quali nuovi tipi di esperienze saranno possibili? Come funzionerà tutto questo in pratica? I modelli genereranno interfacce come codice o produrranno direttamente pixel grezzi?
Non conosco ancora queste risposte. Dovremo sperimentare e scoprirlo!Che cosa significherebbe trattare l'IA come uno strumento invece che come una persona?
Dall’avvio di ChatGPT, le esplorazioni in due direzioni hanno preso velocità.
La prima direzione riguarda le capacità tecniche. Quanto grande possiamo addestrare un modello? Quanto bene può rispondere alle domande del SAT? Con quanta efficienza possiamo distribuirlo?
La seconda direzione riguarda il design dell’interazione. Come comunichiamo con un modello? Come possiamo usarlo per un lavoro utile? Quale metafora usiamo per ragionare su di esso?
La prima direzione è ampiamente seguita e enormemente finanziata, e per una buona ragione: i progressi nelle capacità tecniche sono alla base di ogni possibile applicazione. Ma la seconda è altrettanto cruciale per il campo e ha enormi incognite. Siamo solo a pochi anni dall’inizio dell’era dei grandi modelli. Quali sono le probabilità che abbiamo già capito i modi migliori per usarli?
Propongo una nuova modalità di interazione, in cui i modelli svolgano il ruolo di applicazioni informatiche (ad esempio app per telefoni): fornendo un’interfaccia grafica, interpretando gli input degli utenti e aggiornando il loro stato. In questa modalità, invece di essere un “agente” che utilizza un computer per conto dell’essere umano, l’IA può fornire un ambiente informatico più ricco e potente che possiamo utilizzare.
Metafore per l’interazione
Al centro di un’interazione c’è una metafora che guida le aspettative di un utente su un sistema. I primi giorni dell’informatica hanno preso metafore come “scrivanie”, “macchine da scrivere”, “fogli di calcolo” e “lettere” e le hanno trasformate in equivalenti digitali, permettendo all’utente di ragionare sul loro comportamento. Puoi lasciare qualcosa sulla tua scrivania e tornare a prenderlo; hai bisogno di un indirizzo per inviare una lettera. Man mano che abbiamo sviluppato una conoscenza culturale di questi dispositivi, la necessità di queste particolari metafore è scomparsa, e con esse i design di interfaccia skeumorfici che le rafforzavano. Come un cestino o una matita, un computer è ora una metafora di se stesso.
La metafora dominante per i grandi modelli oggi è modello-come-persona. Questa è una metafora efficace perché le persone hanno capacità estese che conosciamo intuitivamente. Implica che possiamo avere una conversazione con un modello e porgli domande; che il modello possa collaborare con noi su un documento o un pezzo di codice; che possiamo assegnargli un compito da svolgere da solo e che tornerà quando sarà finito.
Tuttavia, trattare un modello come una persona limita profondamente il nostro modo di pensare all’interazione con esso. Le interazioni umane sono intrinsecamente lente e lineari, limitate dalla larghezza di banda e dalla natura a turni della comunicazione verbale. Come abbiamo tutti sperimentato, comunicare idee complesse in una conversazione è difficile e dispersivo. Quando vogliamo precisione, ci rivolgiamo invece a strumenti, utilizzando manipolazioni dirette e interfacce visive ad alta larghezza di banda per creare diagrammi, scrivere codice e progettare modelli CAD. Poiché concepiamo i modelli come persone, li utilizziamo attraverso conversazioni lente, anche se sono perfettamente in grado di accettare input diretti e rapidi e di produrre risultati visivi. Le metafore che utilizziamo limitano le esperienze che costruiamo, e la metafora modello-come-persona ci impedisce di esplorare il pieno potenziale dei grandi modelli.
Per molti casi d’uso, e specialmente per il lavoro produttivo, credo che il futuro risieda in un’altra metafora: modello-come-computer.
Usare un’IA come un computer
Sotto la metafora modello-come-computer, interagiremo con i grandi modelli seguendo le intuizioni che abbiamo sulle applicazioni informatiche (sia su desktop, tablet o telefono). Nota che ciò non significa che il modello sarà un’app tradizionale più di quanto il desktop di Windows fosse una scrivania letterale. “Applicazione informatica” sarà un modo per un modello di rappresentarsi a noi. Invece di agire come una persona, il modello agirà come un computer.
Agire come un computer significa produrre un’interfaccia grafica. Al posto del flusso lineare di testo in stile telescrivente fornito da ChatGPT, un sistema modello-come-computer genererà qualcosa che somiglia all’interfaccia di un’applicazione moderna: pulsanti, cursori, schede, immagini, grafici e tutto il resto. Questo affronta limitazioni chiave dell’interfaccia di chat standard modello-come-persona:
Scoperta. Un buon strumento suggerisce i suoi usi. Quando l’unica interfaccia è una casella di testo vuota, spetta all’utente capire cosa fare e comprendere i limiti del sistema. La barra laterale Modifica in Lightroom è un ottimo modo per imparare l’editing fotografico perché non si limita a dirti cosa può fare questa applicazione con una foto, ma cosa potresti voler fare. Allo stesso modo, un’interfaccia modello-come-computer per DALL-E potrebbe mostrare nuove possibilità per le tue generazioni di immagini.
Efficienza. La manipolazione diretta è più rapida che scrivere una richiesta a parole. Per continuare l’esempio di Lightroom, sarebbe impensabile modificare una foto dicendo a una persona quali cursori spostare e di quanto. Ci vorrebbe un giorno intero per chiedere un’esposizione leggermente più bassa e una vibranza leggermente più alta, solo per vedere come apparirebbe. Nella metafora modello-come-computer, il modello può creare strumenti che ti permettono di comunicare ciò che vuoi più efficientemente e quindi di fare le cose più rapidamente.
A differenza di un’app tradizionale, questa interfaccia grafica è generata dal modello su richiesta. Questo significa che ogni parte dell’interfaccia che vedi è rilevante per ciò che stai facendo in quel momento, inclusi i contenuti specifici del tuo lavoro. Significa anche che, se desideri un’interfaccia più ampia o diversa, puoi semplicemente richiederla. Potresti chiedere a DALL-E di produrre alcuni preset modificabili per le sue impostazioni ispirati da famosi artisti di schizzi. Quando clicchi sul preset Leonardo da Vinci, imposta i cursori per disegni prospettici altamente dettagliati in inchiostro nero. Se clicchi su Charles Schulz, seleziona fumetti tecnicolor 2D a basso dettaglio.
Una bicicletta della mente proteiforme
La metafora modello-come-persona ha una curiosa tendenza a creare distanza tra l’utente e il modello, rispecchiando il divario di comunicazione tra due persone che può essere ridotto ma mai completamente colmato. A causa della difficoltà e del costo di comunicare a parole, le persone tendono a suddividere i compiti tra loro in blocchi grandi e il più indipendenti possibile. Le interfacce modello-come-persona seguono questo schema: non vale la pena dire a un modello di aggiungere un return statement alla tua funzione quando è più veloce scriverlo da solo. Con il sovraccarico della comunicazione, i sistemi modello-come-persona sono più utili quando possono fare un intero blocco di lavoro da soli. Fanno le cose per te.
Questo contrasta con il modo in cui interagiamo con i computer o altri strumenti. Gli strumenti producono feedback visivi in tempo reale e sono controllati attraverso manipolazioni dirette. Hanno un overhead comunicativo così basso che non è necessario specificare un blocco di lavoro indipendente. Ha più senso mantenere l’umano nel loop e dirigere lo strumento momento per momento. Come stivali delle sette leghe, gli strumenti ti permettono di andare più lontano a ogni passo, ma sei ancora tu a fare il lavoro. Ti permettono di fare le cose più velocemente.
Considera il compito di costruire un sito web usando un grande modello. Con le interfacce di oggi, potresti trattare il modello come un appaltatore o un collaboratore. Cercheresti di scrivere a parole il più possibile su come vuoi che il sito appaia, cosa vuoi che dica e quali funzionalità vuoi che abbia. Il modello genererebbe una prima bozza, tu la eseguirai e poi fornirai un feedback. “Fai il logo un po’ più grande”, diresti, e “centra quella prima immagine principale”, e “deve esserci un pulsante di login nell’intestazione”. Per ottenere esattamente ciò che vuoi, invierai una lista molto lunga di richieste sempre più minuziose.
Un’interazione alternativa modello-come-computer sarebbe diversa: invece di costruire il sito web, il modello genererebbe un’interfaccia per te per costruirlo, dove ogni input dell’utente a quell’interfaccia interroga il grande modello sotto il cofano. Forse quando descrivi le tue necessità creerebbe un’interfaccia con una barra laterale e una finestra di anteprima. All’inizio la barra laterale contiene solo alcuni schizzi di layout che puoi scegliere come punto di partenza. Puoi cliccare su ciascuno di essi, e il modello scrive l’HTML per una pagina web usando quel layout e lo visualizza nella finestra di anteprima. Ora che hai una pagina su cui lavorare, la barra laterale guadagna opzioni aggiuntive che influenzano la pagina globalmente, come accoppiamenti di font e schemi di colore. L’anteprima funge da editor WYSIWYG, permettendoti di afferrare elementi e spostarli, modificarne i contenuti, ecc. A supportare tutto ciò è il modello, che vede queste azioni dell’utente e riscrive la pagina per corrispondere ai cambiamenti effettuati. Poiché il modello può generare un’interfaccia per aiutare te e lui a comunicare più efficientemente, puoi esercitare più controllo sul prodotto finale in meno tempo.
La metafora modello-come-computer ci incoraggia a pensare al modello come a uno strumento con cui interagire in tempo reale piuttosto che a un collaboratore a cui assegnare compiti. Invece di sostituire un tirocinante o un tutor, può essere una sorta di bicicletta proteiforme per la mente, una che è sempre costruita su misura esattamente per te e il terreno che intendi attraversare.
Un nuovo paradigma per l’informatica?
I modelli che possono generare interfacce su richiesta sono una frontiera completamente nuova nell’informatica. Potrebbero essere un paradigma del tutto nuovo, con il modo in cui cortocircuitano il modello di applicazione esistente. Dare agli utenti finali il potere di creare e modificare app al volo cambia fondamentalmente il modo in cui interagiamo con i computer. Al posto di una singola applicazione statica costruita da uno sviluppatore, un modello genererà un’applicazione su misura per l’utente e le sue esigenze immediate. Al posto della logica aziendale implementata nel codice, il modello interpreterà gli input dell’utente e aggiornerà l’interfaccia utente. È persino possibile che questo tipo di interfaccia generativa sostituisca completamente il sistema operativo, generando e gestendo interfacce e finestre al volo secondo necessità.
All’inizio, l’interfaccia generativa sarà un giocattolo, utile solo per l’esplorazione creativa e poche altre applicazioni di nicchia. Dopotutto, nessuno vorrebbe un’app di posta elettronica che occasionalmente invia email al tuo ex e mente sulla tua casella di posta. Ma gradualmente i modelli miglioreranno. Anche mentre si spingeranno ulteriormente nello spazio di esperienze completamente nuove, diventeranno lentamente abbastanza affidabili da essere utilizzati per un lavoro reale.
Piccoli pezzi di questo futuro esistono già. Anni fa Jonas Degrave ha dimostrato che ChatGPT poteva fare una buona simulazione di una riga di comando Linux. Allo stesso modo, websim.ai utilizza un LLM per generare siti web su richiesta mentre li navighi. Oasis, GameNGen e DIAMOND addestrano modelli video condizionati sull’azione su singoli videogiochi, permettendoti di giocare ad esempio a Doom dentro un grande modello. E Genie 2 genera videogiochi giocabili da prompt testuali. L’interfaccia generativa potrebbe ancora sembrare un’idea folle, ma non è così folle.
Ci sono enormi domande aperte su come apparirà tutto questo. Dove sarà inizialmente utile l’interfaccia generativa? Come condivideremo e distribuiremo le esperienze che creiamo collaborando con il modello, se esistono solo come contesto di un grande modello? Vorremmo davvero farlo? Quali nuovi tipi di esperienze saranno possibili? Come funzionerà tutto questo in pratica? I modelli genereranno interfacce come codice o produrranno direttamente pixel grezzi?
Non conosco ancora queste risposte. Dovremo sperimentare e scoprirlo!
Tradotto da:\ https://willwhitney.com/computing-inside-ai.htmlhttps://willwhitney.com/computing-inside-ai.html
-
-
 @ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03
@ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 1d7ff02a:d042b5be
2025-05-28 04:02:47
@ 1d7ff02a:d042b5be
2025-05-28 04:02:47For those who still don't truly understand Bitcoin, it means you still don't understand what money is, who creates it, and why humans need money.
It's a scam that the education system doesn't teach this important subject, while we spend almost our entire lives trying to earn money. Therefore, I recommend following the money and studying Bitcoin seriously.
Why Bitcoin Matters
Saving is the greatest discovery in human history
Before humans learned to save, we were just animals living day to day. Saving is what makes humans different from other animals — the ability to think about the future and store for later.
Saving created civilization itself
Without saving, there would be no cities, no science, no art. Everything we call "progress" comes from the ability to save.
Money is the greatest creation in human history
It is the tool that has allowed human civilization to advance to this day. Money is the best tool humans use for saving.
Bitcoin is the best money ever created
It is the most perfect money humans have ever created. No one can control, manipulate, destroy it, and it is truly limited like time in life.
Bitcoin is like a black hole
That will absorb all value from the damaged financial system. It will draw stability and value to itself. Everything of value will flow into Bitcoin eventually.
Bitcoin is like Buddhism discovering truth
It helps understand the root problems of the current financial system and the emergence of many problems in society, just like Buddha who understood all suffering and the causes of suffering.
Bitcoin is freedom
Money is power, money controls human behavior. When we have money that preserves value and cannot be controlled, we will have intellectual freedom, freedom of expression, and the power to choose.
The debt that humanity has created today would take another thousand years to pay off completely
There is no way out and it's heading toward serious collapse. Bitcoin is the light that will help prevent humanity from entering another dark age.
Bitcoin cannot steal your time
It cannot be created from nothing. Every Bitcoin requires real energy and time to create.
Bitcoin is insurance that protects against mismanagement
It helps protect against currency debasement, economic depression, and failed policies. Bitcoin will protect your value.
Bitcoin is going to absorb the world's value
Eventually, Bitcoin will become the store of value for the entire world. It will absorb wealth from all assets, all prices, and all investments.
Exit The Matrix
We live in a financial Matrix. Every day we wake up and go to work, thinking we're building a future for ourselves. But in reality, we're just giving energy to a system that extracts value from us every second. Bitcoin is the red pill — it will open your eyes to see the truth of the financial world. Central banks are the architects of this Matrix — they create money from nothing, and we have to work hard to get it.
The education system has deceived us greatly. They teach us to work for money, but never teach us what money is. We spend 12-16 years in school, then spend our entire lives earning money, but never know what it is, who creates it, and why it has value. This is the biggest scam in human history.
We are taught to be slaves of the system, but not taught to understand the system.
The Bitcoin standard will end war
When you can't print money for war anymore, war becomes too expensive.
We are entering the Bitcoin Renaissance era
An era of financial and intellectual revival. Bitcoin is creating a new class of humans. People who understand and hold Bitcoin will become a new class with true freedom.
The Path to Financial Truth
Follow the money trail and you will see the truth: - Who controls money printing? - Why do prices keep getting higher? - Why are the poor getting poorer and the rich getting richer?
All the answers lie in understanding money and Bitcoin.
Studying Bitcoin is not just about investment — it's about understanding the future of currency and human society.
Don't just work for money. Understand money. Study Bitcoin.
If you don't understand money, you will be a slave to the system forever. If you understand Bitcoin, you will gain freedom.
-
 @ e6817453:b0ac3c39
2024-12-07 15:06:43
@ e6817453:b0ac3c39
2024-12-07 15:06:43I started a long series of articles about how to model different types of knowledge graphs in the relational model, which makes on-device memory models for AI agents possible.
We model-directed graphs
Also, graphs of entities
We even model hypergraphs
Last time, we discussed why classical triple and simple knowledge graphs are insufficient for AI agents and complex memory, especially in the domain of time-aware or multi-model knowledge.
So why do we need metagraphs, and what kind of challenge could they help us to solve?
- complex and nested event and temporal context and temporal relations as edges
- multi-mode and multilingual knowledge
- human-like memory for AI agents that has multiple contexts and relations between knowledge in neuron-like networks
MetaGraphs
A meta graph is a concept that extends the idea of a graph by allowing edges to become graphs. Meta Edges connect a set of nodes, which could also be subgraphs. So, at some level, node and edge are pretty similar in properties but act in different roles in a different context.
Also, in some cases, edges could be referenced as nodes.
This approach enables the representation of more complex relationships and hierarchies than a traditional graph structure allows. Let’s break down each term to understand better metagraphs and how they differ from hypergraphs and graphs.Graph Basics
- A standard graph has a set of nodes (or vertices) and edges (connections between nodes).
- Edges are generally simple and typically represent a binary relationship between two nodes.
- For instance, an edge in a social network graph might indicate a “friend” relationship between two people (nodes).
Hypergraph
- A hypergraph extends the concept of an edge by allowing it to connect any number of nodes, not just two.
- Each connection, called a hyperedge, can link multiple nodes.
- This feature allows hypergraphs to model more complex relationships involving multiple entities simultaneously. For example, a hyperedge in a hypergraph could represent a project team, connecting all team members in a single relation.
- Despite its flexibility, a hypergraph doesn’t capture hierarchical or nested structures; it only generalizes the number of connections in an edge.
Metagraph
- A metagraph allows the edges to be graphs themselves. This means each edge can contain its own nodes and edges, creating nested, hierarchical structures.
- In a meta graph, an edge could represent a relationship defined by a graph. For instance, a meta graph could represent a network of organizations where each organization’s structure (departments and connections) is represented by its own internal graph and treated as an edge in the larger meta graph.
- This recursive structure allows metagraphs to model complex data with multiple layers of abstraction. They can capture multi-node relationships (as in hypergraphs) and detailed, structured information about each relationship.
Named Graphs and Graph of Graphs
As you can notice, the structure of a metagraph is quite complex and could be complex to model in relational and classical RDF setups. It could create a challenge of luck of tools and software solutions for your problem.
If you need to model nested graphs, you could use a much simpler model of Named graphs, which could take you quite far.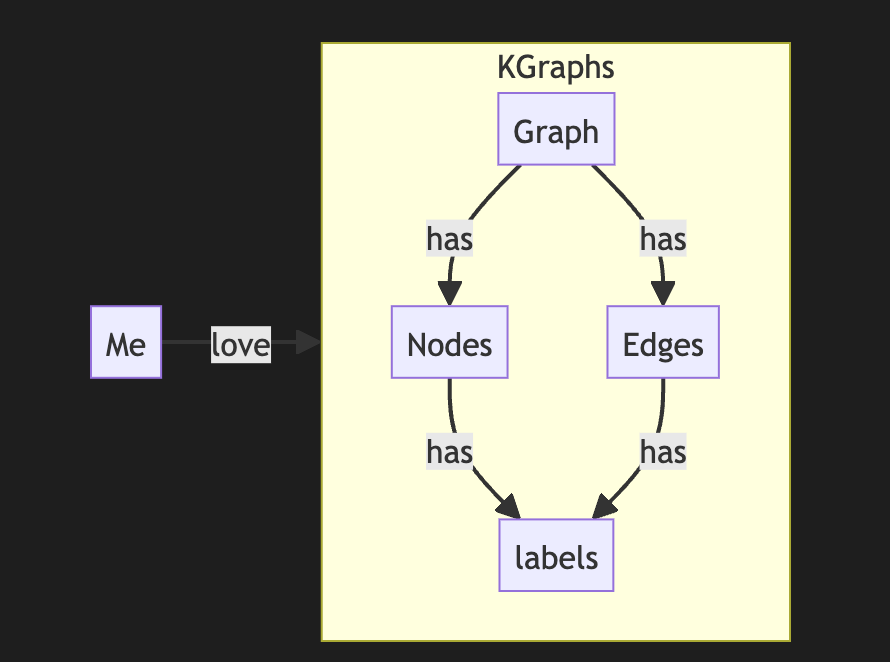
The concept of the named graph came from the RDF community, which needed to group some sets of triples. In this way, you form subgraphs inside an existing graph. You could refer to the subgraph as a regular node. This setup simplifies complex graphs, introduces hierarchies, and even adds features and properties of hypergraphs while keeping a directed nature.
It looks complex, but it is not so hard to model it with a slight modification of a directed graph.
So, the node could host graphs inside. Let's reflect this fact with a location for a node. If a node belongs to a main graph, we could set the location to null or introduce a main node . it is up to you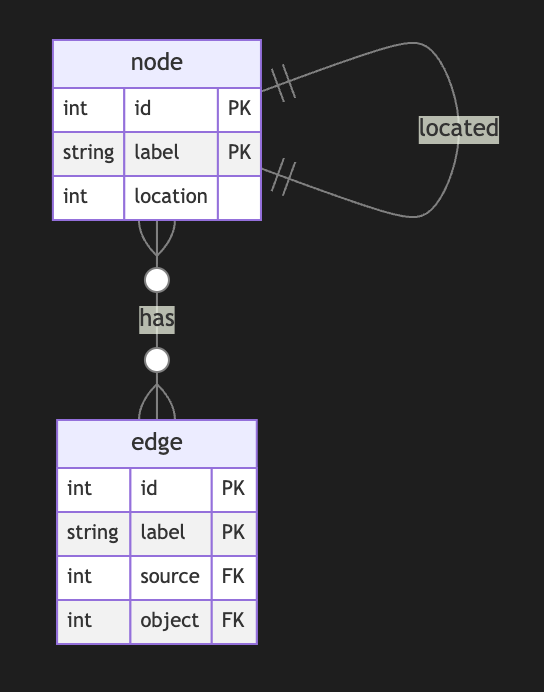
Nodes could have edges to nodes in different subgraphs. This structure allows any kind of nesting graphs. Edges stay location-free
Meta Graphs in Relational Model
Let’s try to make several attempts to model different meta-graphs with some constraints.
Directed Metagraph where edges are not used as nodes and could not contain subgraphs
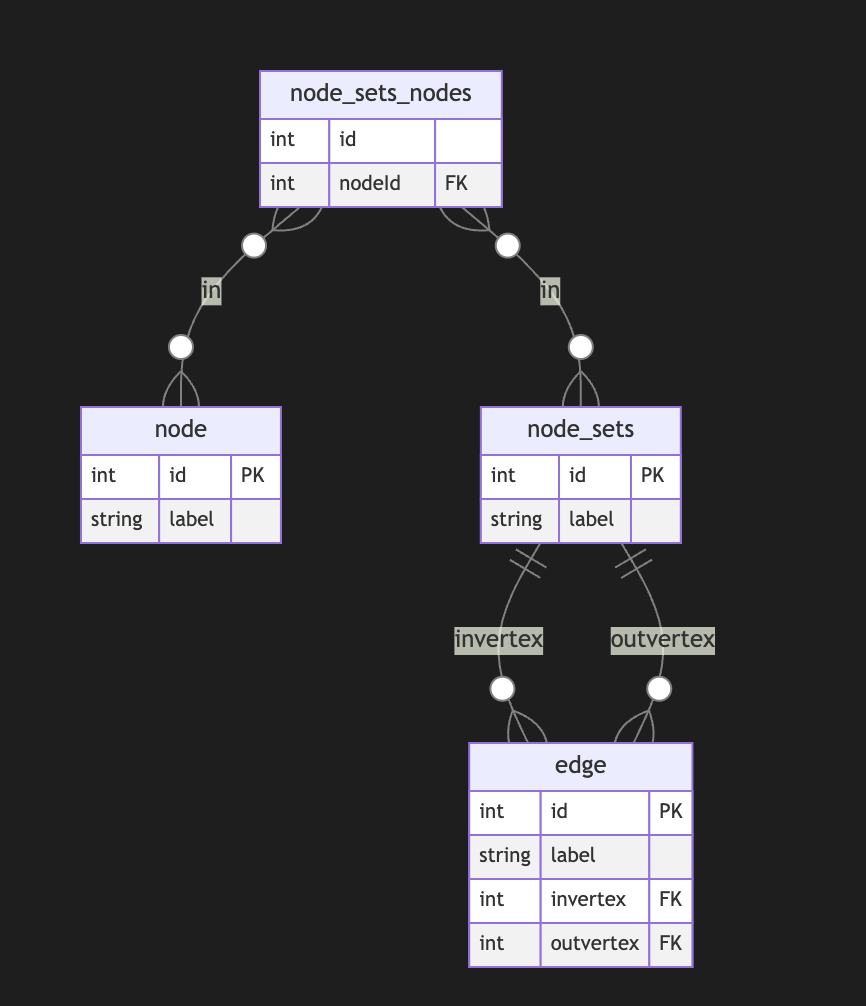
In this case, the edge always points to two sets of nodes. This introduces an overhead of creating a node set for a single node. In this model, we can model empty node sets that could require application-level constraints to prevent such cases.
Directed Metagraph where edges are not used as nodes and could contain subgraphs
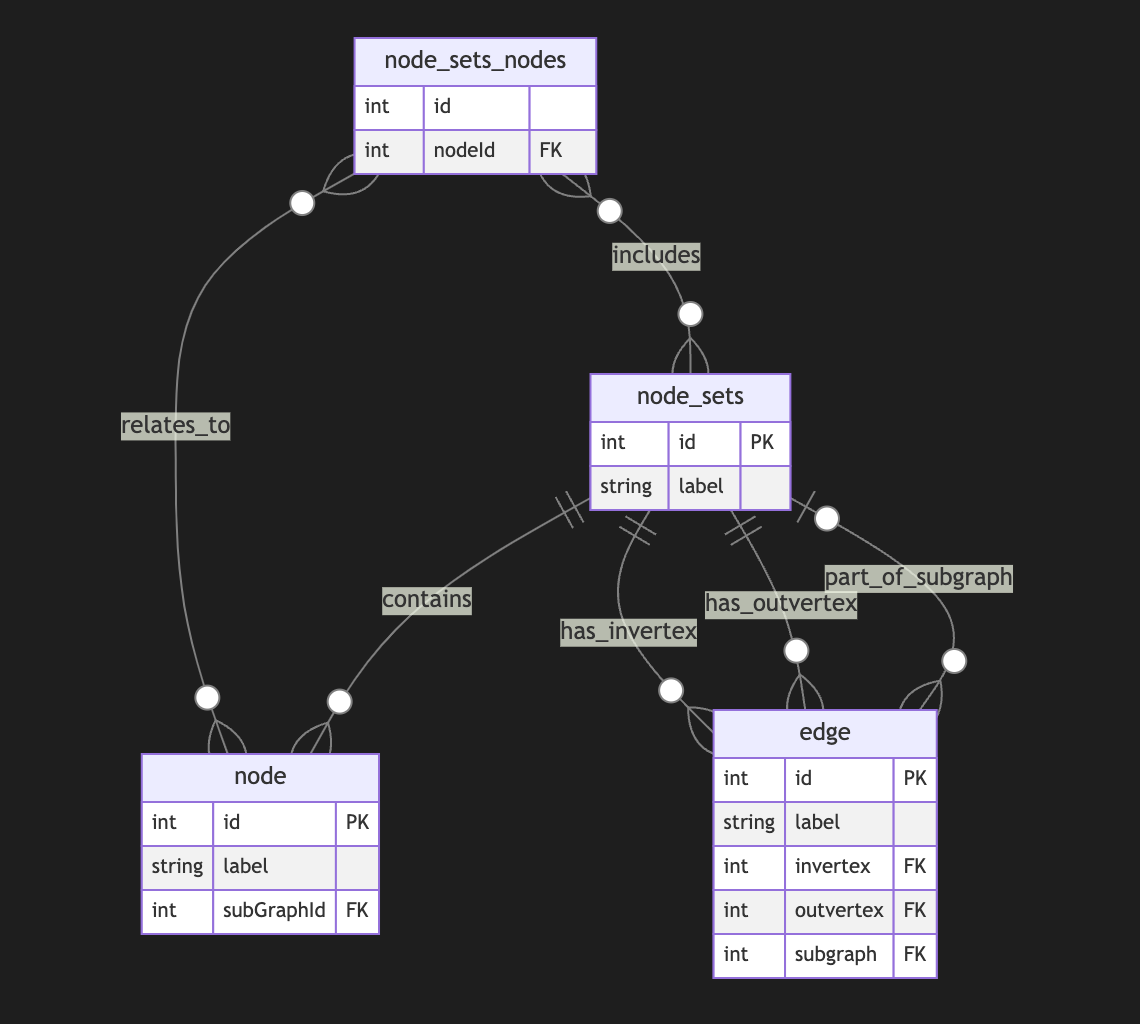
Adding a node set that could model a subgraph located in an edge is easy but could be separate from in-vertex or out-vert.
I also do not see a direct need to include subgraphs to a node, as we could just use a node set interchangeably, but it still could be a case.Directed Metagraph where edges are used as nodes and could contain subgraphs
As you can notice, we operate all the time with node sets. We could simply allow the extension node set to elements set that include node and edge IDs, but in this case, we need to use uuid or any other strategy to differentiate node IDs from edge IDs. In this case, we have a collision of ephemeral edges or ephemeral nodes when we want to change the role and purpose of the node as an edge or vice versa.
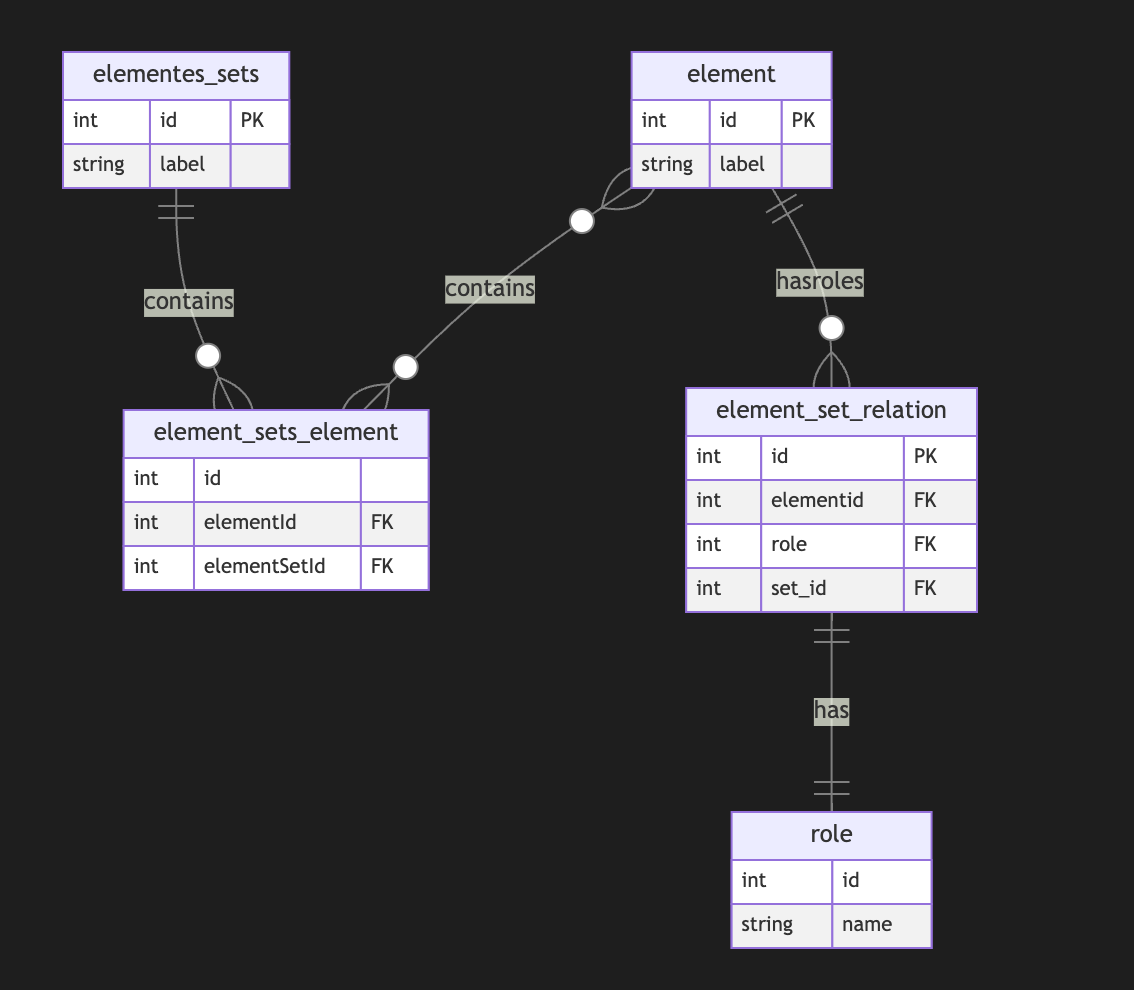
A full-scale metagraph model is way too complex for a relational database.
So we need a better model.Now, we have more flexibility but loose structural constraints. We cannot show that the element should have one vertex, one vertex, or both. This type of constraint has been moved to the application level. Also, the crucial question is about query and retrieval needs.
Any meta-graph model should be more focused on domain and needs and should be used in raw form. We did it for a pure theoretical purpose. -
 @ 502ab02a:a2860397
2025-05-28 02:03:01
@ 502ab02a:a2860397
2025-05-28 02:03:01ยังมีอีกสิ่งหนึ่งที่มักซ่อนอยู่ในเมล็ดธัญพืช ถั่วเปลือกแข็ง และพืชตระกูลถั่วทั้งหลาย เป็นเหมือน “กล่องเก็บขุมทรัพย์” สำหรับชีวิตน้อยๆ ของพืชในวันที่จะเติบโต แต่พอสิ่งนี้หลุดเข้ามาในร่างกายมนุษย์ มันกลับถูกมองว่าเป็น “ขโมย” ขโมยแร่ธาตุไปจากร่างกายเรา เจ้าสิ่งนั้นคือ “กรดไฟติก” หรือ phytic acid นั่นเองครับ
กรดไฟติกเป็นสารอินทรีย์ที่พืชสร้างขึ้นเพื่อเก็บสะสมฟอสฟอรัสไว้ใช้ตอนงอกงามในอนาคต มันเปรียบเหมือนกระปุกออมสินของเมล็ดพืช พวกเมล็ดถั่วดำ ข้าวโพด ข้าวกล้อง ข้าวโอ๊ต เมล็ดทานตะวัน อัลมอนด์ ไปจนถึงเต้าหู้ ถั่วเหลือง และธัญพืชต่างๆ ล้วนมีกรดไฟติกอยู่ไม่น้อย โดยเฉพาะถ้าเป็น “ธัญพืชเต็มเมล็ด” ที่ไม่ผ่านการขัดสีแบบที่หลายๆคนชอบ นั่นเพราะเยื่อหุ้มเมล็ดคือที่เก็บเจ้าตัวนี้ไว้
หลายคนคงคิดว่า อ้าวแล้วเจ้ากรดไฟติกทำไมถึงมีชื่อเสียงไม่ค่อยดีนัก? คำตอบอยู่ที่ “ความสามารถในการจับแร่ธาตุ” ของมันนี่แหละครับ
กรดไฟติกเป็นเหมือนแม่เหล็กเล็กๆ ที่สามารถจับตัวกับแร่ธาตุต่างๆ ได้ดี โดยเฉพาะ “แร่ธาตุบวกสอง” ทั้งหลาย แร่ธาตุบวกสอง คือ แร่ธาตุที่เวลาอยู่ในร่างกายจะอยู่ในรูปของไอออนที่มีประจุไฟฟ้า บวก 2 (เขียนว่า ²⁺) หรือพูดอีกแบบคือ มันเสียอิเล็กตรอนออกไป 2 ตัว เลยกลายเป็นไอออนที่มีพลังบวก 2 หน่วย กรดไฟติก หรือ แทนนิน จะทำตัวเป็น "แม่เหล็ก" ดูดแร่ธาตุออกไป มันมักจะจับกับแร่ธาตุที่มีประจุบวก โดยเฉพาะพวกที่ประจุบวกแรงๆ แบบ บวกสอง (²⁺) นี่แหละ เพราะจับแน่น จับเหนียว ยิ่งบวกเยอะยิ่งจับดี เหมือนแช่แม่เหล็กลงไปในกล่องโลหะ เช่น ธาตุเหล็ก สังกะสี แมกนีเซียม แคลเซียม และทองแดง พอมันจับเสร็จแล้ว ร่างกายเราก็ไม่สามารถดูดซึมแร่ธาตุพวกนี้เข้าไปได้ เพราะมันเปลี่ยนสภาพกลายเป็นของจับคู่ที่ลำไส้ไม่รู้จัก ไม่รู้จะพาเข้าร่างกายยังไง สุดท้ายก็ต้องโบกมือลาไปพร้อมของเสีย
พวกที่เป็น บวกสาม (³⁺) อย่างเช่น อลูมิเนียม (Al³⁺) หรือ เหล็กเฟอริก (Fe³⁺) จะจับแน่นมาก ถึงขั้นอาจเกิด “ตกตะกอน” แบบไม่ละลายน้ำเลยทีเดียว พวกนี้ลำไส้ไม่สามารถดูดซึมได้เลย ในขณะที่แร่ธาตุบวกหนึ่ง โซเดียม (Na⁺) โพแทสเซียม (K⁺) ประจุบวกแค่ +1 จับกับกรดไฟติกได้น้อยกว่า
ในแง่นี้กรดไฟติกเลยถูกเรียกว่า “สารต้านสารอาหาร” หรือ anti-nutrient เพราะมันต้านไม่ให้ร่างกายได้แร่ธาตุที่ควรจะได้ แต่อย่าเพิ่งตัดสินมันเหมือนผู้ร้าย เพราะในขณะที่กรดไฟติกอาจขโมยแร่ธาตุบางตัวจากร่างกาย มันก็มีคุณสมบัติน่าสนใจที่ดูจะเป็นคุณงามความดีของมันเหมือนกัน เช่น มันสามารถจับกับโลหะหนักบางชนิด เช่น ตะกั่ว หรือแคดเมียม ที่อาจปนเปื้อนในอาหาร แล้วพาออกไปจากร่างกายก่อนที่สิ่งเหล่านั้นจะทำร้ายเรา
และอีกด้านหนึ่งที่กำลังเป็นที่สนใจคือ ฤทธิ์ต้านอนุมูลอิสระของกรดไฟติก มันอาจช่วยลดการอักเสบ หรือยับยั้งการเติบโตของเซลล์มะเร็งบางชนิดในระดับเซลล์ได้ มีงานวิจัยที่พบว่ามันอาจไปจับกับธาตุเหล็กส่วนเกินที่ว่ายอยู่ในเลือด ซึ่งเป็นตัวเร่งปฏิกิริยาอนุมูลอิสระ คล้ายช่วย “เก็บเศษเหล็กที่ลอยไปมาบนทางด่วนหลอดเลือด” ให้ปลอดภัยขึ้นอีกนิด
แต่ทั้งนี้ทั้งนั้น อยากให้คิดแบบนี้ครับว่า กรดไฟติกคือคนแปลกหน้าที่ “บางมื้อก็มีประโยชน์ บางมื้อก็ทำให้เราขาดของดี” สิ่งสำคัญอยู่ที่ “สภาวะแวดล้อมของมื้ออาหาร” ถ้าอาหารในมื้อมีแร่ธาตุไม่มากนัก แล้วกรดไฟติกเข้ามาเยอะ มันก็ยิ่งลดโอกาสดูดซึมแร่ธาตุเหล่านั้น แต่ถ้ามื้ออาหารมีความหลากหลาย โปรตีนเพียงพอ วิตามิน C อยู่ครบ ก็ช่วยเพิ่มการดูดซึมธาตุเหล็กได้ดีขึ้น เพราะมันเปลี่ยนเหล็กให้อยู่ในรูปแบบที่ร่างกายดูดซึมง่ายขึ้น
แล้วเราจะจัดการยังไงกับกรดไฟติกในครัวแบบบ้านเรา?
วิธีพื้นบ้านมีมาแต่โบราณแล้วนั่นคือ -แช่น้ำ ก่อนหุงข้าวกล้อง หรือแช่ถั่วก่อนนำไปต้ม จะช่วยลดกรดไฟติกได้ระดับหนึ่ง เพราะมีเอนไซม์ที่ชื่อว่า phytase ซึ่งจะเริ่มทำงานเมื่อพืชได้รับน้ำและอุณหภูมิพอเหมาะ -การหมัก เช่น หมักแป้งข้าวเปลือกทำขนม หรือการหมักเต้าหู้ ก็เป็นวิธีดั้งเดิมที่ช่วยลดกรดไฟติกลงได้มาก เพราะเอนไซม์ของจุลินทรีย์ในกระบวนการหมักจะช่วยย่อยกรดไฟติกให้ลดลง -การงอก หรือ sprouting คือการทำให้เมล็ดพืชเริ่มต้นชีวิตใหม่ เช่น ถั่วงอก ข้าวกล้องงอก วิธีนี้ลดกรดไฟติกได้ดีมาก เพราะ phytase ที่อยู่ในพืชจะถูกกระตุ้นให้ทำงานสูงสุดตอนพืชเริ่มงอก
ข้อมูลคร่าวๆ บอกว่า วิธีเหล่านี้อาจลดกรดไฟติกลงได้ 30-90% ขึ้นกับชนิดของพืช และระยะเวลาที่ใช้
แต่ต้องรู้ไว้ด้วยว่า… การลดกรดไฟติกก็อาจทำให้พลังงานสำรองหรือสารอาหารบางตัวในพืชหายไปด้วยเช่นกัน เช่น วิตามิน B และสารต้านอนุมูลอิสระบางชนิด จึงควรใช้วิธีที่พอเหมาะ ไม่ถึงกับฆ่าความดีของพืชหมด
ดังนั้นเช่นกันครับว่า กรดไฟติกไม่ใช่ศัตรู ไม่ใช่เทพเจ้า แต่คือ “สมการ” ที่ต้องรู้จักแก้ไขให้เหมาะกับมื้ออาหารของเรา ถ้าเฮียเลือกกินแบบ animal-based อยู่แล้ว แร่ธาตุสำคัญส่วนใหญ่ก็ได้จากเนื้อสัตว์แบบที่ดูดซึมได้ดีอยู่แล้ว กรดไฟติกจากพืชที่กินพอประมาณก็อาจไม่ได้ร้ายแรงอะไรนัก เพียงแต่ต้องรู้ทันและจัดการให้พอดี ไม่ให้มันกลายเป็นตัวฉุดไม่ให้ร่างกายดูดซึมของดี
สุดท้าย เหมือนชีวิตเรานี่แหละ… “ทุกอย่างมีมุมมืดและมุมสว่าง อยู่ที่ว่าเราจัดแสงยังไงให้แม้แต่เงาก็กลายเป็นพลังของชีวิตเรา” #โรงบ่มสุขภาพ #HealthyHut #pirateketo #ตำรับเอ๋ #siripun #siamstr
/เฮียเอง
-
 @ 33baa074:3bb3a297
2025-05-28 08:25:13
@ 33baa074:3bb3a297
2025-05-28 08:25:13The oil-in-water sensoris an instrument specially used to detect oil substances in water bodies. Its working principle is mainly based on the characteristic that oil substances will produce fluorescence under ultraviolet light. The following is a detailed explanation:
Principle Overview The oil-in-water sensor uses the characteristic that oil substances will produce fluorescence under ultraviolet light, and measures the fluorescence intensity to infer the concentration of oil substances. Specifically, the sensor uses ultraviolet light as the excitation light source to irradiate the water sample to be tested. After the oil substance absorbs ultraviolet light, it will stimulate fluorescence, and the fluorescence signal is received by the photo detector and converted into an electrical signal. By measuring the strength of the electrical signal, the concentration of oil substances in the water sample can be inferred.
Workflow Ultraviolet light irradiation: The ultraviolet light source inside the sensor emits ultraviolet light and irradiates it into the water sample to be tested.
Fluorescence generation: After the oil substance in the water sample absorbs ultraviolet light, it will stimulate fluorescence.
Fluorescence detection: The photo detector in the sensor measures the intensity of this fluorescence.
Signal conversion: The signal processing circuit converts the output of the photo detector into an electrical signal proportional to the amount of oil in the water. Data analysis: By analyzing the strength of the electrical signal, the concentration of oil substances in the water sample can be obtained.
Features and applications The oil in water sensor has high sensitivity and can detect soluble and falsifiable oils. It is suitable for a variety of water quality monitoring scenarios, such as oil field monitoring, industrial circulating water, condensate water, wastewater treatment, surface water stations, etc. In addition, it can also monitor the content of crude oil (benzene and benzene homologous) in water sources such as reservoirs and water plants in real time online, play an early warning role, and protect the safety of water sources.
Practical application The oil in water sensor has a wide range of functions in practical applications, including but not limited to the following aspects: Monitoring the water quality of water sources: ensuring the safety of drinking water, and timely discovering pollution sources and ensuring water supply safety by continuously monitoring oil substances in water sources. Monitoring sewage treatment plant emissions: ensuring that the discharge water quality of sewage treatment plants meets the emission standards to avoid secondary pollution to the environment. Monitoring rivers, lakes and other water bodies: assessing the pollution status and providing a basis for pollution control. Early warning and emergency response: It has real-time monitoring and early warning functions, and can issue an alarm in time when abnormal conditions are found, providing valuable time for emergency response and reducing losses caused by pollution. Scientific research: Through the monitoring data of this sensor, we can deeply understand the distribution, migration and transformation of oil substances in water bodies, and provide a scientific basis for environmental protection and governance.
In summary, the oil in water sensor monitors the oil content in water bodies through ultraviolet fluorescence method, has high sensitivity and broad application prospects, and is an indispensable and important tool in modern environmental monitoring and industrial production.
-
 @ b83a28b7:35919450
2025-05-16 19:23:58
@ b83a28b7:35919450
2025-05-16 19:23:58This article was originally part of the sermon of Plebchain Radio Episode 110 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ 33baa074:3bb3a297
2025-05-28 08:10:17
@ 33baa074:3bb3a297
2025-05-28 08:10:17The control of residual chlorine in swimming pools is an important part of water quality management, which aims to ensure the sanitation and safety of swimming pool water while avoiding discomfort to swimmers. Here are some key points about residual chlorine control in swimming pools:
Standards for residual chlorine According to the regulations of the national health supervision department, the residual chlorine in swimming pool water should be kept between 0.3mg/L-1.5mg/L. This range can not only ensure effective disinfection, but also avoid irritation to swimmers' skin and eyes caused by excessive residual chlorine. Too low residual chlorine will lead to incomplete disinfection and increase the risk of bacterial growth; while too high residual chlorine may cause human discomfort and even poisoning.
 The role of residual chlorine
Residual chlorine is a residual disinfectant in swimming pool water, usually in the form of sodium hypocrite (NaClO). It has strong oxidizing properties and can effectively kill bacteria, viruses and other microorganisms in water, thereby ensuring the health of swimmers. In addition, residual chlorine can eliminate harmful substances such as organic matter and ammonia in water to keep the water clean.
The role of residual chlorine
Residual chlorine is a residual disinfectant in swimming pool water, usually in the form of sodium hypocrite (NaClO). It has strong oxidizing properties and can effectively kill bacteria, viruses and other microorganisms in water, thereby ensuring the health of swimmers. In addition, residual chlorine can eliminate harmful substances such as organic matter and ammonia in water to keep the water clean.Residual chlorine detection method The method of detecting residual chlorine in swimming pools usually uses test strips or test kits for qualitative or quantitative detection. In addition, online monitoring instruments can be used to monitor the residual chlorine in the swimming pool in real time. These methods can help managers promptly detect and deal with situations where the residual chlorine content is too high or too low, ensuring that the water quality of the swimming pool meets the standards.
Methods for controlling residual chlorine Reasonable addition of disinfectants: According to the water quality of the swimming pool and the number of swimmers, reasonable addition of disinfectants to control the residual chlorine content within the specified range.
Regular testing: Regularly test the residual chlorine in the swimming pool to promptly detect and deal with situations where the residual chlorine content is too high or too low.
Maintain swimming pool equipment: Regularly check and maintain swimming pool equipment to ensure the water treatment effect and circulation filtration are normal, and reduce residual disinfectants and other harmful substances in the water.
Do a good job in swimmer hygiene management: Strengthen swimmer hygiene management, require swimmers to shower and rinse their feet before entering the pool, and reduce pollution sources entering the swimming pool.
Solution for excessive residual chlorine If the residual chlorine content in the swimming pool exceeds the standard range, the following measures can be taken:
Use decorating agent: Use decorating agent to quickly restore the excessive residual chlorine in the swimming pool to the normal range (0.3~0.5mg/L). This method is applicable to excessive residual chlorine caused by excessive addition of chlorine disinfectant.
Adjust the water treatment process: According to the water quality, adjust the water treatment process appropriately, such as selecting the appropriate type and dosage of disinfectant, and adjusting operating parameters such as flow rate, pH value, etc., to reduce the generation of residual chlorine.
Strengthen equipment maintenance: Regularly maintain and maintain the water treatment equipment of the swimming pool to ensure its normal operation and disinfection effect.
Through the above methods, the residual chlorine content in the swimming pool can be effectively controlled to ensure water quality safety and protect the health of swimmers.
-
 @ da0b9bc3:4e30a4a9
2025-05-28 08:07:30
@ da0b9bc3:4e30a4a9
2025-05-28 08:07:30Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
https://stacker.news/items/991020
-
 @ eb0157af:77ab6c55
2025-05-28 08:01:35
@ eb0157af:77ab6c55
2025-05-28 08:01:35Bitcoin surpasses gold in the United States: 50 million holders and a dominant role in the global market.
According to a new report by River, for the first time in history, the number of Americans owning bitcoin has surpassed that of gold holders. The analysis reveals that approximately 50 million U.S. citizens currently own the cryptocurrency, while gold owners number 37 million. In fact, 14.3% of Americans own bitcoin, the highest percentage of holders worldwide.

Source: River
The report highlights that 40% of all Bitcoin-focused companies are based in the United States, consolidating America’s dominant position in the sector. Additionally, 40.5% of Bitcoin holders are men aged 31 to 35, followed by 35.9% of men aged 41 to 45. In contrast, only 13.4% of holders are women.

Source: River
Notably, U.S. companies hold 94.8% of all bitcoins owned by publicly traded companies worldwide. According to the report, recent regulatory changes in the U.S. have made the asset more accessible through financial products such as spot ETFs.
The document also shows that American investors increasingly view the cryptocurrency as protection against fiscal instability and inflation, appreciating its limited supply and decentralized governance model.
For River, Bitcoin offers significant practical advantages over gold in the modern digital era. Its ease of custody, cross-border transfer, and liquidity make the cryptocurrency an attractive option for both individual and institutional investors, the report suggests.
The post USA: 50 million Americans own bitcoin appeared first on Atlas21.
-
 @ e6817453:b0ac3c39
2024-12-07 15:03:06
@ e6817453:b0ac3c39
2024-12-07 15:03:06Hey folks! Today, let’s dive into the intriguing world of neurosymbolic approaches, retrieval-augmented generation (RAG), and personal knowledge graphs (PKGs). Together, these concepts hold much potential for bringing true reasoning capabilities to large language models (LLMs). So, let’s break down how symbolic logic, knowledge graphs, and modern AI can come together to empower future AI systems to reason like humans.
The Neurosymbolic Approach: What It Means ?
Neurosymbolic AI combines two historically separate streams of artificial intelligence: symbolic reasoning and neural networks. Symbolic AI uses formal logic to process knowledge, similar to how we might solve problems or deduce information. On the other hand, neural networks, like those underlying GPT-4, focus on learning patterns from vast amounts of data — they are probabilistic statistical models that excel in generating human-like language and recognizing patterns but often lack deep, explicit reasoning.
While GPT-4 can produce impressive text, it’s still not very effective at reasoning in a truly logical way. Its foundation, transformers, allows it to excel in pattern recognition, but the models struggle with reasoning because, at their core, they rely on statistical probabilities rather than true symbolic logic. This is where neurosymbolic methods and knowledge graphs come in.
Symbolic Calculations and the Early Vision of AI
If we take a step back to the 1950s, the vision for artificial intelligence was very different. Early AI research was all about symbolic reasoning — where computers could perform logical calculations to derive new knowledge from a given set of rules and facts. Languages like Lisp emerged to support this vision, enabling programs to represent data and code as interchangeable symbols. Lisp was designed to be homoiconic, meaning it treated code as manipulatable data, making it capable of self-modification — a huge leap towards AI systems that could, in theory, understand and modify their own operations.
Lisp: The Earlier AI-Language
Lisp, short for “LISt Processor,” was developed by John McCarthy in 1958, and it became the cornerstone of early AI research. Lisp’s power lay in its flexibility and its use of symbolic expressions, which allowed developers to create programs that could manipulate symbols in ways that were very close to human reasoning. One of the most groundbreaking features of Lisp was its ability to treat code as data, known as homoiconicity, which meant that Lisp programs could introspect and transform themselves dynamically. This ability to adapt and modify its own structure gave Lisp an edge in tasks that required a form of self-awareness, which was key in the early days of AI when researchers were exploring what it meant for machines to “think.”
Lisp was not just a programming language—it represented the vision for artificial intelligence, where machines could evolve their understanding and rewrite their own programming. This idea formed the conceptual basis for many of the self-modifying and adaptive algorithms that are still explored today in AI research. Despite its decline in mainstream programming, Lisp’s influence can still be seen in the concepts used in modern machine learning and symbolic AI approaches.
Prolog: Formal Logic and Deductive Reasoning
In the 1970s, Prolog was developed—a language focused on formal logic and deductive reasoning. Unlike Lisp, based on lambda calculus, Prolog operates on formal logic rules, allowing it to perform deductive reasoning and solve logical puzzles. This made Prolog an ideal candidate for expert systems that needed to follow a sequence of logical steps, such as medical diagnostics or strategic planning.
Prolog, like Lisp, allowed symbols to be represented, understood, and used in calculations, creating another homoiconic language that allows reasoning. Prolog’s strength lies in its rule-based structure, which is well-suited for tasks that require logical inference and backtracking. These features made it a powerful tool for expert systems and AI research in the 1970s and 1980s.
The language is declarative in nature, meaning that you define the problem, and Prolog figures out how to solve it. By using formal logic and setting constraints, Prolog systems can derive conclusions from known facts, making it highly effective in fields requiring explicit logical frameworks, such as legal reasoning, diagnostics, and natural language understanding. These symbolic approaches were later overshadowed during the AI winter — but the ideas never really disappeared. They just evolved.
Solvers and Their Role in Complementing LLMs
One of the most powerful features of Prolog and similar logic-based systems is their use of solvers. Solvers are mechanisms that can take a set of rules and constraints and automatically find solutions that satisfy these conditions. This capability is incredibly useful when combined with LLMs, which excel at generating human-like language but need help with logical consistency and structured reasoning.
For instance, imagine a scenario where an LLM needs to answer a question involving multiple logical steps or a complex query that requires deducing facts from various pieces of information. In this case, a solver can derive valid conclusions based on a given set of logical rules, providing structured answers that the LLM can then articulate in natural language. This allows the LLM to retrieve information and ensure the logical integrity of its responses, leading to much more robust answers.
Solvers are also ideal for handling constraint satisfaction problems — situations where multiple conditions must be met simultaneously. In practical applications, this could include scheduling tasks, generating optimal recommendations, or even diagnosing issues where a set of symptoms must match possible diagnoses. Prolog’s solver capabilities and LLM’s natural language processing power can make these systems highly effective at providing intelligent, rule-compliant responses that traditional LLMs would struggle to produce alone.
By integrating neurosymbolic methods that utilize solvers, we can provide LLMs with a form of deductive reasoning that is missing from pure deep-learning approaches. This combination has the potential to significantly improve the quality of outputs for use-cases that require explicit, structured problem-solving, from legal queries to scientific research and beyond. Solvers give LLMs the backbone they need to not just generate answers but to do so in a way that respects logical rigor and complex constraints.
Graph of Rules for Enhanced Reasoning
Another powerful concept that complements LLMs is using a graph of rules. A graph of rules is essentially a structured collection of logical rules that interconnect in a network-like structure, defining how various entities and their relationships interact. This structured network allows for complex reasoning and information retrieval, as well as the ability to model intricate relationships between different pieces of knowledge.
In a graph of rules, each node represents a rule, and the edges define relationships between those rules — such as dependencies or causal links. This structure can be used to enhance LLM capabilities by providing them with a formal set of rules and relationships to follow, which improves logical consistency and reasoning depth. When an LLM encounters a problem or a question that requires multiple logical steps, it can traverse this graph of rules to generate an answer that is not only linguistically fluent but also logically robust.
For example, in a healthcare application, a graph of rules might include nodes for medical symptoms, possible diagnoses, and recommended treatments. When an LLM receives a query regarding a patient’s symptoms, it can use the graph to traverse from symptoms to potential diagnoses and then to treatment options, ensuring that the response is coherent and medically sound. The graph of rules guides reasoning, enabling LLMs to handle complex, multi-step questions that involve chains of reasoning, rather than merely generating surface-level responses.
Graphs of rules also enable modular reasoning, where different sets of rules can be activated based on the context or the type of question being asked. This modularity is crucial for creating adaptive AI systems that can apply specific sets of logical frameworks to distinct problem domains, thereby greatly enhancing their versatility. The combination of neural fluency with rule-based structure gives LLMs the ability to conduct more advanced reasoning, ultimately making them more reliable and effective in domains where accuracy and logical consistency are critical.
By implementing a graph of rules, LLMs are empowered to perform deductive reasoning alongside their generative capabilities, creating responses that are not only compelling but also logically aligned with the structured knowledge available in the system. This further enhances their potential applications in fields such as law, engineering, finance, and scientific research — domains where logical consistency is as important as linguistic coherence.
Enhancing LLMs with Symbolic Reasoning
Now, with LLMs like GPT-4 being mainstream, there is an emerging need to add real reasoning capabilities to them. This is where neurosymbolic approaches shine. Instead of pitting neural networks against symbolic reasoning, these methods combine the best of both worlds. The neural aspect provides language fluency and recognition of complex patterns, while the symbolic side offers real reasoning power through formal logic and rule-based frameworks.
Personal Knowledge Graphs (PKGs) come into play here as well. Knowledge graphs are data structures that encode entities and their relationships — they’re essentially semantic networks that allow for structured information retrieval. When integrated with neurosymbolic approaches, LLMs can use these graphs to answer questions in a far more contextual and precise way. By retrieving relevant information from a knowledge graph, they can ground their responses in well-defined relationships, thus improving both the relevance and the logical consistency of their answers.
Imagine combining an LLM with a graph of rules that allow it to reason through the relationships encoded in a personal knowledge graph. This could involve using deductive databases to form a sophisticated way to represent and reason with symbolic data — essentially constructing a powerful hybrid system that uses LLM capabilities for language fluency and rule-based logic for structured problem-solving.
My Research on Deductive Databases and Knowledge Graphs
I recently did some research on modeling knowledge graphs using deductive databases, such as DataLog — which can be thought of as a limited, data-oriented version of Prolog. What I’ve found is that it’s possible to use formal logic to model knowledge graphs, ontologies, and complex relationships elegantly as rules in a deductive system. Unlike classical RDF or traditional ontology-based models, which sometimes struggle with complex or evolving relationships, a deductive approach is more flexible and can easily support dynamic rules and reasoning.
Prolog and similar logic-driven frameworks can complement LLMs by handling the parts of reasoning where explicit rule-following is required. LLMs can benefit from these rule-based systems for tasks like entity recognition, logical inferences, and constructing or traversing knowledge graphs. We can even create a graph of rules that governs how relationships are formed or how logical deductions can be performed.
The future is really about creating an AI that is capable of both deep contextual understanding (using the powerful generative capacity of LLMs) and true reasoning (through symbolic systems and knowledge graphs). With the neurosymbolic approach, these AIs could be equipped not just to generate information but to explain their reasoning, form logical conclusions, and even improve their own understanding over time — getting us a step closer to true artificial general intelligence.
Why It Matters for LLM Employment
Using neurosymbolic RAG (retrieval-augmented generation) in conjunction with personal knowledge graphs could revolutionize how LLMs work in real-world applications. Imagine an LLM that understands not just language but also the relationships between different concepts — one that can navigate, reason, and explain complex knowledge domains by actively engaging with a personalized set of facts and rules.
This could lead to practical applications in areas like healthcare, finance, legal reasoning, or even personal productivity — where LLMs can help users solve complex problems logically, providing relevant information and well-justified reasoning paths. The combination of neural fluency with symbolic accuracy and deductive power is precisely the bridge we need to move beyond purely predictive AI to truly intelligent systems.
Let's explore these ideas further if you’re as fascinated by this as I am. Feel free to reach out, follow my YouTube channel, or check out some articles I’ll link below. And if you’re working on anything in this field, I’d love to collaborate!
Until next time, folks. Stay curious, and keep pushing the boundaries of AI!
-
 @ 866e0139:6a9334e5
2025-05-22 06:46:34
@ 866e0139:6a9334e5
2025-05-22 06:46:34Autor: Jana Moava. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Zwei Worte nur braucht man – und die Sache ist klar. Jeder gebildete Russe kennt diese Worte: sie stammen aus dem XIX. Jahrhundert, als Nikolaus I. die Krim-Kampagne begann und das Zarenreich nach üblen Querelen ganz Europa und die Türkei zum Gegner hatte - allen voran die Herrscher der Weltmeere: das British Empire mit Queen Victoria. Der historische Ausdruck anglitschanka gadit (locker übersetzt: die Engländerin macht Shit) besitzt bis heute verdeckte politische Sprengkraft und ist seit Ende Februar 2022 in Russland wieder populär. Wer auch immer der Urheber dieser im Original durchaus diskreten Benennung des Fäkalvorgangs war: der Ausdruck steht für ernste Konflikte mit dem Englisch sprechenden Westen, dem Erzfeind.
Ein kurzer Blick in die Geschichte mag dies erläutern: Fast alle westlichen Historiker benennen als Auslöser des Krimkrieges Mitte des IX. Jahrhunderts die Verteidigung der russisch-orthodoxen Kirche und deren Zugang zur Kreuzkirche in Jerusalem. Es wird vom letzten Kreuzzug u.a. geschrieben. Das ist eine höchst einseitige Interpretation, denn es ging Nikolaus I. vor allem um den Zugang zum einzigen dauerhaft eisfreien Hafen Russlands im Schwarzen Meer, durch die Meeresenge der Dardanellen ins Mittelmeer. Das ist verständlich, war doch die Eroberung der Krim ab 1783 unter seiner Großmutter Katharina II. aus eben diesem Grunde erfolgt. Damals schon wurde der Hafen Sewastopol zum Stützpunkt der russischen Flotte ausgebaut.
Ende 1825, nach dem plötzlichen Tod des ältesten Bruders Alexander I., war Nikolaus von seiner Erziehung her auf eine Regentschaft ganz und gar nicht vorbereitet gewesen, doch herrschte er dreißig Jahre lang nicht nur über das russische Reich, sondern auch über Finnland und das damalige Königreich Polen unter russischem Protektorat. Nikolaus I. zeichnete sich von Beginn an durch Gewaltmaßnahmen aus: Als ihm im Dezember (russ. dekabr)1825 eine Gruppe sehr gebildeter, freiheitsliebender junger Adligen aus besten Familien den Eid verweigerte (dies zog als Dekabristenaufstand in die Geschichte ein), ließ er fünf der Rebellen hängen, die anderen schickte er in Fußfesseln nach Sibirien in die Bergwerke. Er gründete die berüchtigte Geheimpolizei Dritte Abteilung, ließ Privatbriefe des Dichters Puschkin öffnen (obwohl dieser „in seiner Gnade stand“) und Historikern ist Nikolaus I. als Gendarm Europas bekannt. Im russischen Volk aber nannte man ihn kurz und bündig: *Nicki Knüppel aus dem Sack (Nikolaschka palkin). *
Leo Tolstoj beschrieb diesen Zaren in seinen Erzählungen über die Kriege im Kaukasus (Hadschi Murat) als feist und fett, mit leblosen, trüben Augen und als berüchtigten Frauenjäger. Tolstoj war es auch, der als junger Teilnehmer im Krimkrieg drei Erzählungen schrieb: Sewastopol im Dezember 1854, im Mai 1855 und im August 1855. Nachdem das British Empire unter Queen Victoria Russland den Krieg erklärt hatte (in Koalition mit Frankreich und Piemont-Sardinien als Schutzmacht des Osmanischen Reiches), entstand der Ausdruck anglitschanka gadit – die Engländerin macht Shit. Bis heute findet man dazu drastische Illustrationen im Netz…
Noch bevor russische Truppen Ende Februar 2022 in die Ukraine marschierten, lebte dieser Ausdruck in Russland wieder auf. Wer hierzulande Interesse an der Wahrheit hat, kann deutliche Parallelen zur damaligen politischen Lage entdecken, auch in Bezug auf die Verhaltensweisen des derzeitigen russischen Staatschefs und des historischen Nicki Knüppel aus dem Sack. Obwohl der amtierende durchaus Anerkennung verdient hat, denn nach dem Zusammenbruch der Sowjetunion in den 1990er Jahren unter Jelzin stellte er die Staatlich-keit des verlotterten, hungernden Landes wieder her und trieb den wirtschaftlichen Aufbau voran. Davon kann ich zeugen, lebte ich doch von 1992 – 2008 vor Ort.
Sicher - heute ist längst bekannt, daß die bereits Ende März 2022 in Istanbul laufenden Friedensverhandlungen zwischen Russland und der Ukraine vom britischen Premier und im Namen des US Präsidenten boykottiert wurden. Daniel Ruch, Schweizer Botschafter a.D., sprach gar von Sabotage! Der deutsche General a. D. Harald Kujat kommentierte damals mit den Worten: „Seit April 2022 gehen alle Kriegsopfer in der Ukraine auf das Konto des Westens!“ Der Ausdruck anglitschanka gadit ist seitdem in Russland wieder geläufig. Nun, brandaktuell, treffen sich die Kriegsparteien wieder in Istanbul: Ausgang ungewiss. Doch wird inzwischen auch von einzelnen westlichen Politikern anerkannt, dass Russland eine neutrale Pufferzone zu den Nato-Staaten verlangt und braucht.
Wenn hierzulande gemutmaßt wird, alle Russen würden den Ukraine-Krieg bejahen, so sollte man zur Kenntnis nehmen, dass derartige Aussagen kaum die wirkliche Überzeugung wiedergeben. Seit den Repressionen unter Stalin, seit in jeder zweiten Familie nahe Angehörige im GULAG einsaßen und umkamen und darüber Jahrzehnte lang geschwiegen werden musste, ist der Wahrheitsgehalt öffentlicher Umfragen getrost zu bezweifeln. Hat man hier etwa vergessen, dass seit 2011 auf eine mächtig wachsende zivile Protestbewegung und riesige Demonstrationen in russischen Großstädten immer schärfere Aktionen von Seiten des Staates erfolgten? Dass Knüppel auf Köpfe und Leiber prasselten, wie zur Zeit Nickis I., und der Polizeiapparat derart wuchs, dass heute das Verhältnis von Bürger und Silowiki (Vertreter der Gewalt)1:1 steht?
Offenbar weiß man hier nicht, dass schon Anfang 2022 von Mitarbeitern in jeder staatlich finanzierten Institution, ob im Bereich von Kultur, Wissenschaft, Forschung oder Lehre die schriftliche Zustimmung zur Spezialoperation mit der Ukraine eingefordert wurde! Eine Weigerung hatte den Verlust des Arbeitsplatzes zur Folge, egal welches Renommée oder welchen Rang der Betroffene besaß! Manche Leiter von staatlichen Institutionen zeigten dabei gehöriges Geschick und zeichneten für alle; andere (z.B. staatliche Theater) riefen jeden Mitarbeiter ins Kontor. Nur wenige Personen, die unter dem persönlichem Schutz des Präsidenten standen, konnten sich dieser Zustimmung zum Krieg entziehen. Wissenschaftler und Künstler emigrierten zuhauf. Berlin ist voll mit Geflohenen aus jenem Land, das kriegerisch ins Bruderland einmarschierte! Aber kann denn jeder emigrieren? Die Alten, Familien mit Kindern? Mit guten Freunden, die dort blieben, ist eine Kommunikation nur verschlüsselt möglich, in Nachrichten wie: die Feuer der Inquisition brennen (jeder, der von der offiziellen Doktrin abweicht, ist gefährdet), Ratten verbreiten Krankheiten bezieht sich auf Denunziationen, die in jeder Diktatur aufblühen, wenn sich jemand dem Schussfeld entziehen möchte und im vorauseilenden Gehorsam den Nachbarn anzeigt. Kennen wir das nicht noch aus unseren hitlerdeutschen 1930er Jahren?!
Je mehr im Reich aller Russen in den letzten Jahren von oben geknebelt und geknüppelt wurde, desto mehr Denunziationen griffen um sich. Junge Menschen, die auf Facebook gegen den Krieg posteten, wurden verhaftet. Seit 2023 sitzen u.a. zwei junge russische Theaterfrauen aufgrund der üblen Denunziation eines Kollegen hinter Gittern. Die Inszenierung der Regisseurin Zhenja Berkowitsch und der Autorin Swetlana Petritschuk erhielt Ende 2022 den höchsten Theaterpreis von ganz Russland, die Goldene Maske. Das Stück Finist (Phönix), klarer Falke ist nach dem Motiv eines russischen Märchens geschrieben, fußt aber auf dokumentarischem Material: es verhandelt die Versuchung junger Frauen, auf Islamisten hereinzufallen und sie aus Frust und falsch verstandener Solidarität zu heiraten. Die Anklage hat den Spieß genau umgedreht: Autorin und Regisseurin wurden des Terrorismus beschuldigt! Das Rechtssystem im Land scheint heute noch vergleichbar mit jenem, das Alexander Puschkin vor über 200 Jahren in seiner Erzählung Dubrowski authentisch beschrieb: Wer die Macht hat, regelt das Recht. Man kann die Erzählung des russischen Robin Hood auch deutsch nachlesen (leider, leider hat Puschkin sie nicht beendet).
Andere, erbaulichere Elemente aus der Zeit Puschkins, bzw. von Nikolaus I., dienen allerdings als Gegengewicht zum Alltag: seit Ende 2007 finden in Moskau und St. Petersburg jeden Winter nach dem Vorbild der historischen Adelsbälle große gesellschaftliche Events statt: Puschkinball, Wiener Opernball, jetzt nur noch Opernball genannt. Der Nachwuchs aus begüterten Familien lernt alte Tanzschritte und feine Sitten. Fort mit dem sowjetischen Schmuddelimage! Prächtige Kostümbälle werden nun zum Abschluss jedes Schuljahres aufgeboten. In stilisierten Kostümen der Zeit Nikolajs I. bzw. Puschkins tanzen Schuldirektoren, Lehrer und junge Absolventen. Der Drang nach altem Glanz und Größe (oder eine notwendige Kompensation?) spiegelt sich im Volk.
Werfen wir jedoch einen Blick auf einige Geschehnisse in der Ukraine ab 2014, die in unserer Presse immer noch verschwiegen werden: Im Spätsommer 2022 begegnete ich auf Kreta einer Ukrainerin aus der Nordukraine, die wegen des fürchterlichen Nationalismus nach 2014 ihre Heimat verließ. Sie ist nicht die einzige! Ihre Kinder waren erwachsen und zogen nach Polen, sie aber reiste mit einer Freundin weiter Richtung Griechenland, lernte die Sprache, erwarb die Staatsbürgerschaft und ist nun auf Kreta verheiratet.
Natalia erzählte mir, was bei uns kaum zu lesen ist, was jedoch Reporter wie Patrick Baab oder Historiker wie Daniele Ganser schon lange berichtet haben: 2014, als die Bilder der Proteste auf dem Maidan um die Welt gingen, habe die damalige amerikanische Regierung unter Präsident Biden die Vorgänge in Kiew für einen Putsch genutzt: Janukowitsch, der korrupte, doch demokratisch gewählte Präsident der Ukraine wurde gestürzt, die Ereignisse mit Hilfe von Strohmännern und rechten Nationalisten gelenkt, die mit Geld versorgt wurden. Bis es zum Massaker auf dem Maidan kam, als bewaffnete, ihrer Herkunft nach zunächst nicht identifi-zierbare Schützen (es waren v.a. rechte Nationalisten, so der gebürtige Ukrainer und US Bürger Professor N. Petro und Prof. Ivan Katchanovskij) von den Dächern in die Menge schossen.
Im YouTube Kanal Neutrality Studies konnte man am 17.02.2024 hören: Anlässlich des traurigen 10. Jahrestages des Maidan-Massakers, bei dem am 20. Februar 2014 mehr als 100 Menschen durch Scharfschützenfeuer getötet wurden, spreche ich heute mit Ivan Katchanovski, einem ukrainischen (und kanadischen) Politikwissenschaftler an der Univer-sität von Ottawa, der das Massaker detailliert erforscht hat. Letztes Jahr veröffentlichte er das Papier „Die Maidan-Massaker-Prozess und Untersuchungserkenntnisse: Implikationen für den Krieg zwischen der Ukraine und Russland und die Beziehungen“. Kurz gesagt, das Massaker wurde NICHT von den Kräften Victor Janukowytschs begangen, wie in westlichen Medien berichtet, und es gibt schlüssige Beweise dafür, dass die Schützen Teil des ultra-rechten Flügels der Ukraine waren, die dann nach dem Putsch an die Macht kamen. (Link zum Paper).
Wer erinnert sich hierzulande noch daran, dass 2014 im deutschen öffentlichen Fernsehen von Hunter Biden, Sohn des US-Präsidenten berichtet wurde, der durch dubiose Gas- und Ölgeschäfte in der Ukraine auffiel? Dass damals im deutschen Fernsehen auch Bilder von Ukrainern mit SS-Stahlhelmen auftauchten? In einer Arte-Reportage zu Hilfs-transporten im März 2022 aus Polen über die Westukraine konnte der aufmerksame Zu-schauer an fast allen Häusern die tiefroten Banner von Anhängern des verstorbenen, in München begrabenen, faschistischen Stepan Bandera erkennen. Ausgesprochen wurde es nicht.
Die neue Kreterin Natalia sprach auch über eine Amerikanerin ukrainischer Herkunft, die Röntgenärztin Uljana Suprun, die aus den USA als Gesundheitsministerin rekrutiert wurde und unter dem amerikafreundlichen Präsidenten Poroschenko von 2016-2019 diesen Posten innehatte. Was bitte sollte eine Röntgenärztin aus den USA auf dem Ministerposten der Ukraine?! Streit und Skandal umgaben sie fast täglich in der RADA, dem ukrainischen Parlament. Es wurde gemunkelt, sie diene als Feigenblatt bei der Herstellung biologischer Waffen. Material zu ihr ist bis heute auf YouTube zu finden.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Natalia bezeichnete die ukrainischen Emigrantenkreise in den USA und Kanada zurecht als ultranationalistisch, sie seien Kollaborateure der Nazis bei der Judenvernichtung gewesen und hätten sich nach dem Rückzug der Deutschen rechtzeitig nach Übersee abgesetzt. Das ist wohl bekannt.
Heute ist das Recherchieren der wahren Geschehnisse von 2014 zwar immer noch mühsam, aber die Wahrheit sickert immer mehr durch, zumal auch Exilukrainer dazu geschrieben und öffentlich gesprochen haben. Die Kanäle SaneVox und Neutrality studies liefern unermüdlich weitere Fakten! Im März 2025 klärte der US-Professor Jeffrey Sachs das Europa-Parlament endlich in allen Details über die kriegerischen Machenschaften bestimmter Kreise innerhalb der englischsprechenden Westmächte auf!
Kürzlich war im multipolar-magazin zu lesen, wie erschreckend tief unser eigenes Land bereits in**** den Ukraine-Krieg verwickelt ist: Da hieß es:
*„Kriegsplanung von deutschem Boden“ *
Zwei umfassende Beiträge der „New York Times“ und der Londoner „Times“ belegen, was lange bestritten wurde: die tiefe militärische und strategische Verwicklung von Nato-Mitgliedsstaaten in den Ukraine-Krieg. Demnach wird deren Kriegsbeteiligung seit Jahren vom europäischen Hauptquartier der US-Armee in Wiesbaden koordiniert. Für Deutschland stellen sich damit verfassungsrechtliche Fragen.
Und ein Karsten Montag schrieb ebenda am 25. April 2025:
Mehr als drei Jahre nach Beginn des russisch-ukrainischen Krieges berichten zwei große westliche Tageszeitungen über die tiefgreifende Beteiligung von Nato-Militärs an diesem Konflikt. Den Anfang machte die „New York Times“ (NYT). Unter dem Titel „Die Partnerschaft: Die geheime Geschichte des Krieges in der Ukraine“ erschien Ende März ein umfassender *Artikel, der laut Autor Adam Entous auf 300 Interviews mit Regierungs-, Militär- und Geheim-dienstvertretern in der Ukraine, den Vereinigten Staaten sowie weiteren Nato-Partnern basiert. Es handle sich um die „unerzählte Geschichte“ der „versteckten Rolle“ der USA bei den ukrainischen Militäroperationen. *
Wenige Wochen später veröffentlichte die britische Tageszeitung „The Times“ Anfang April einen ähnlichen Beitrag mit dem Titel „Die unerzählte Geschichte der entscheidenden Rolle der britischen Militärchefs in der Ukraine“. Dieser bestätigt die tiefe Verstrickung der Nato-Staaten in Militäroperationen wie der ukrainischen Offensive 2023. Abweichend vom NYT-Artikel bezeichnet er jedoch die britischen Militärchefs als die „Köpfe“ der „Anti-Putin“-Koalition. Einigkeit herrscht wiederum bei der Frage, wer für den Misserfolg der Operationen verantwortlich ist: Dies sei eindeutig der Ukraine zuzuschreiben. Auch im Times-Beitrag wird auf die besondere Rolle des europäischen US-Hauptquartiers im hessischen Wiesbaden bei der Koordination der Einsätze und den Waffenlieferungen hingewiesen.
Na also! Es gibt unter den aus der Ukraine Geflüchteten hier allerdings eine große Mehrheit, die von diesen Fakten weder etwas wissen, noch wissen wollen. Amerika und die Heimat der Anglitschanka ist für sie das Gelobte Land und wehe, du sprichst darüber, dann wirst du sofort der russischen Propaganda verdächtig. Wie Nicki mittlerweile daheim den Knüppel schwingt, interessiert sie auch nicht.
Wieso wird hier nicht untersucht, wieso wird verschwiegen, dass Alexej Nawalny für einen englischen Dienst arbeitete – woher erhielt er das viele Geld für seine Kampagnen? Wo leben nun seine Witwe und die Kinder? Auf der Insel im nebligen Avalon/ Albion…
Ein letztes Beispiel aus dem Bereich der Kultur zum Verständnis des leider so aktuellen Ausdrucks Die Engländerin macht Shit: Anfang 2024 wurde im staatlichen Sender ONE (ARD) eine Serie der BBC zu frühen Erzählungen von Michail Bulgakow ausgestrahlt:** Aufzeichnungen eines jungen Arztes. Die BBC verhunzte den in Kiew geborenen Arzt und weltberühmten Autor derart, dass dem Zuschauer schlecht wurde: Mit dem Titel A Young Doctor‘s Notebook verfilmte sie Bulgakows frühe Erzählungen über die Nöte eines jungen Arztes in der bettelarmen sowjetrussischen Provinz in den 1920er Jahren hypernaturalistisch, blut-, dreck- und eitertriefend. Pseudokyrillische Titel und Balalaika Geklimper begleiteten das Leiden von schwer traumatisierten Menschen im russischen Bürgerkrieg oder Abscheulichkeiten, wie das Amputieren eines Mädchenbeines mit einer Baumsäge - ausgestrahlt vom 1. Deutschen Fernsehen! Michail Bulgakow hätte sich im Grabe umgedreht.
Als Autor beherrschte Bulgakow die Kunst der Groteske ebenso wie hochlyrische Schilderungen. Seine Prosa und seine Theaterstücke aber wurden Zeit seines Lebens von der Sowjetmacht verstümmelt - und post mortem auch von seinen ukrainischen Landsleuten: sein schönes Museum, das ehemalige Domizil der Familie Bulgakow in Kiew am Andrejew-Steig, das mit seinem ersten Roman Die weiße Garde (Kiew vor 100 Jahren im Strudel auch ultranationalistischer Strömungen) und der berühmten Dramatisierung Die Tage der Turbins in die große Literatur einzog, dieses Museum wurde abgewickelt und geschlossen, weil Bulgakow angeblich schlecht über die Ukraine geschrieben hätte!
Ein Glück jedoch, dass die bedeutenden Werke Bulgakows seit nun drei Dekaden von russischsprachigen Philologen beharrlich in ihrer ursprünglichen Fassung wieder hergestellt wurden. Seine großen Romane Die weiße Garde und Meister und Margarita seien in der hervorragenden deutschen Übersetzung von Alexander Nitzberg jedem Interessierten ans Herz gelegt!
Die obigen Ausführungen sind keinesfalls eine Rechtfertigung des Krieges, es geht vielmehr um Hintergründe, Fakten und Machenschaften, die in der Regel bis heute bei uns verschwiegen werden! Obwohl es nun sonnenklar und öffentlich ist, dass bestimmte Inter-essengruppen der englischsprachigen Westmächte die hochgefährliche Konfrontationspolitik mit Russland zu verantworten haben: die Engländerin macht Shit…Und wir? Wir schweigen, glauben der immer noch laufenden Propaganda und wehren uns nicht gegen diese üble Russenphobie?! Ich erinnere mich noch lebhaft an die Nachkriegszeit im Ruhrgebiet, als der Ton ruppig war und Dreck und Trümmer unsere Sicht beherrschten. Auch uns kleinen Kindern gegenüber wurde von den bösen Russen gesprochen, als hätten diese unser Land überfallen.
Ja – es waren viele Geflüchtete aus dem Osten hier gestrandet, und diese hatten Unsägliches hinter sich. Lew Kopelew, der den Einmarsch der Roten Armee in Ostpreußen miterlebte und Gräuel vergebens zu verhindern suchte, wurde noch im April 1945 verhaftet und wegen Mitleid mit dem Feind zu 10 Jahren Lager verurteilt. Viele Jahre später erschienen seine Erinnerungen Aufbewahren für alle Zeit – auch auf Deutsch. Über die mindestens 27 Mio Opfer in der damaligen Sowjetunion und über die deutschen Aggressoren, die damals mit Mord und Raub die bösen Russen, sowjetische Zivilisten überfielen, wurde in den 1950er Jahren, im zerbombten und dreckigen Pott kein einziges Wort verloren. Der Spieß wurde einfach umgedreht. Von der Blockade Leningrads erfuhr ich erst als Erwachsene, anno 1974, als Austauschstudentin vor Ort.
Exakt vor 10 Jahren wurde es jedoch möglich – herzlichen Dank der damaligen stell-vertretenden tatarischen Kulturministerin Frau Irada Ayupova! – mein dokumentarisches Antikriegsstück mit Schicksalen von Kriegskindern – sowjetischen, jüdischen, deutschen – in Kasan, der Hauptstadt von Tatarstan, zweisprachig auf die Bühne des dortigen Jugendtheaters zu bringen. Wir spielten 15 Vorstellungen und einige tausend Jugendliche im Saal verstummten und verstanden, dass Krieg furchtbar ist. Hier und heute will leider kein Theater das Stück umsetzen…
Wir Menschen brauchen Frieden und keine Aufrüstung für neue Kriege! Der gute alte Aischylos schrieb einst in seinem Stück Die Perser: Wahrheit ist das erste Opfer eines Krieges. Leider ist dies immer noch genauso aktuell wie damals. Pfui Teufel!
Jana Moava (Pseudonym) ist Journalistin, Dozentin und arbeitete für große Zeitungen als Korrespondentin.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 502ab02a:a2860397
2025-05-28 01:57:42
@ 502ab02a:a2860397
2025-05-28 01:57:42ในปี 2013 ณ กรุงลอนดอน แฮมเบอร์เกอร์หน้าตาดูธรรมดาแต่ไม่ธรรมดาชิ้นหนึ่งได้ถูกจัดวางอย่างสง่างามบนจานสีขาวในงานแถลงข่าวระดับโลก ไม่ใช่เพราะมันแพงเกินเหตุที่ตั้งราคาที่ 330,000 ดอลลาร์ต่อชิ้น แต่เพราะมันไม่เคยเกิดขึ้นมาก่อนในประวัติศาสตร์นี่คือ “เนื้อเพาะเลี้ยง” (cultured meat) ชิ้นแรกของโลกที่เติบโตมาจากเซลล์ ไม่ใช่จากสัตว์ทั้งตัว
เบื้องหลังอาหารชิ้นนี้คือชายชาวดัตช์คนหนึ่ง ชื่อว่า มาร์ค โพสต์ (Mark Post) นักวิทยาศาสตร์ด้านสรีรวิทยาหลอดเลือด ซึ่งไม่ได้มีดีกรีจากแค่มหาวิทยาลัย แต่มีความฝันที่อยากจะสร้างอาหารจากเทคโนโลยีเพื่ออนาคต เขาเริ่มต้นจากห้องทดลองเล็กๆ ที่มหาวิทยาลัย Maastricht ในประเทศเนเธอร์แลนด์ โดยเชื่อว่าการเพาะเลี้ยงเนื้อจากเซลล์ต้นกำเนิดของวัวจะสามารถลดผลกระทบด้านสิ่งแวดล้อมจากอุตสาหกรรมเนื้อสัตว์ได้
แต่กว่าจะมีแฮมเบอร์เกอร์เพาะเลี้ยงได้หนึ่งชิ้น เขาต้องเพาะเลี้ยงเส้นใยกล้ามเนื้อเล็กๆ มากกว่า 20,000 เส้น นำมารวมกัน ประกอบโครง สร้างรูปร่าง คล้ายกับงานศิลปะทางวิทยาศาสตร์ ใช้เวลาเป็นเดือน แถมกระบวนการทั้งหมดต้องอยู่ในสภาพปลอดเชื้อราวกับโรงพยาบาลของนาโนเทคโนโลยี ส่วนต้นทุนมหาศาลที่ใช้ในวันนั้น มาจากมหาเศรษฐีผู้ร่วมก่อตั้ง Google อย่าง Sergey Brin ที่เห็นว่ามันอาจเป็นคำตอบของปัญหาอาหารโลกในอนาคต
แต่เรื่องนี้มีอะไรมากกว่าที่สื่อกระแสหลักอยากให้คุณรู้
หลังจากเปิดตัวเนื้อในห้องแล็บ โลกก็เหมือนถูกปลุกให้ตื่นขึ้นในอีกมิติหนึ่ง บริษัทสตาร์ทอัพที่เคยเน้นเขียนโค้ด เริ่มหันมาเขียนสูตรเนื้อ บริษัทรายใหญ่อย่าง Cargill, Tyson Foods และแม้แต่ Richard Branson ก็เทเงินสนับสนุนบริษัทรุ่นใหม่อย่าง Mosa Meat ซึ่งก่อตั้งโดย Dr. Post เองในปี 2016 พร้อมแผนทะเยอทะยานที่จะส่ง “เนื้อจากแล็บ” เข้าซูเปอร์มาร์เก็ตภายในทศวรรษเดียว
Mosa Meat พยายามลดต้นทุนจากหลักแสน ให้เหลือหลักร้อย และวันนี้บริษัทเหล่านี้กำลังสร้างโรงงานที่ผลิตเนื้อในถังหมักขนาดยักษ์ ไม่ต่างจากโรงเบียร์ พวกเขาเลี้ยงเซลล์วัวในน้ำเลี้ยงที่เดิมทีเคยใช้เซรุ่มจากลูกวัว (Fetal Bovine Serum) ซึ่งเป็นสิ่งที่ย้อนแย้ง ที่สวนทางกับภาพ “ปลอดภัยไร้เลือด” มาก เพราะในขณะที่โฆษณาว่า “ปลอดการฆ่า” แต่กลับใช้ส่วนผสมที่ได้มาจากเลือดลูกวัวที่ยังไม่เกิด จนต้องหาทางเปลี่ยนสูตรเป็น “น้ำเลี้ยงเทียม” ที่มาจากสารเคมีและอาหารสังเคราะห์แทน
ด้วยโครงสร้าง scaffold ที่ช่วยให้เซลล์ก่อตัวเป็นเนื้อเยื่อ และ กระบวนการเพาะเลี้ยงใน bioreactor ขนาดยักษ์ ที่เปลี่ยนเซลล์เล็ก ๆ ให้เป็นเนื้อก้อนใหญ่ในเวลาไม่กี่สัปดาห์
แต่ขณะที่ภาพความล้ำซึ่งดูจะเติบโตอย่างสดใส กลับมีเงามืดที่เติบโตพร้อมกันไปเงียบๆไม่ต่างกับอนาคินและดาร์ธเวเดอร์
แม้จะเป็นนวัตกรรมล้ำหน้า แต่ทุกขั้นตอนถูกห่อหุ้มไว้ด้วย “สิทธิบัตร” สิ่งที่ทำให้เนื้อชนิดนี้ไม่ได้เป็นของทุกคน แต่เป็นสมบัติทางปัญญาของบริษัทเท่านั้น เนื้อจากเซลล์เหล่านี้ ไม่เหมือนเนื้อจากฟาร์มที่ใครก็เลี้ยงเองได้ ไม่สามารถเก็บเมล็ดพันธุ์ไว้เพาะรุ่นหน้าแบบชาวนาในอดีต ทุกอย่างต้องเริ่มต้นในห้องแล็บ ต้องใช้เทคโนโลยีเฉพาะ ต้องมีสูตรลับเฉพาะ ต้องพึ่งบริษัทที่มีสิทธิบัตรครอบครองชีวิตเซลล์เพียงไม่กี่เจ้า
Mosa Meat ไม่ได้หยุดแค่การผลิต พวกเขายื่นจด สิทธิบัตรกว่า 10 กลุ่ม ครอบคลุมตั้งแต่สูตรน้ำเลี้ยง วิธีเพาะเลี้ยงเซลล์ ไปจนถึงวิธีห่อบรรจุสินค้าขั้นสุดท้าย กล่าวอีกอย่างคือ ถ้าใครอยากทำเนื้อเพาะเลี้ยงแบบนี้บ้าง ก็ต้อง “จ่ายค่าลิขสิทธิ์” ให้เขาเสียก่อน เรากำลังก้าวสู่ยุคที่ อาหารไม่ใช่ผลผลิตจากดินและแรงคน แต่เป็นผลผลิตของทรัพย์สินทางปัญญา และเมื่อใดที่ “เนื้อ” กลายเป็นสิ่งที่คนผลิตเองไม่ได้ ต้องซื้อจากห้างเท่านั้น เกษตรกรกลายเป็นผู้บริโภค ผู้บริโภคกลายเป็นผู้ขึ้นอยู่กับระบบ ห่วงโซ่อาหารที่เคยเป็นของชุมชนถูกตัดขาดด้วยท่อส่งจากห้องทดลองสู่จานอาหาร เราไม่ได้ซื้อเนื้อ แต่ “เช่าเทคโนโลยี” ที่ผลิตเนื้อมาให้เรากิน
และที่น่าสนใจคือ รัฐบาลในหลายประเทศกลับเป็นผู้ให้ทุนสนับสนุน เช่น โครงการของสหภาพยุโรปที่มอบเงินกว่า 2 ล้านยูโรให้ Dr. Post และ Mosa Meat รวมถึงโครงการของสิงคโปร์ที่ให้ใบอนุญาตจำหน่ายเนื้อเพาะเลี้ยงรายแรกของโลกในปี 2020 ราวกับว่า “เนื้อจากแล็บ” กำลังจะกลายเป็นนโยบายด้านความมั่นคงอาหารแห่งอนาคต
มันไม่ใช่เรื่องของการวิจัยอีกต่อไป แต่มันคือการปูทางอำนาจใหม่ ที่เปลี่ยน “อาหาร” ให้กลายเป็น “ซอฟต์แวร์ชีวภาพ” ที่จดทะเบียนครอบครองสิทธิ์แบบเดียวกับแอปในมือถือ
แล้วการใช้สื่อก็จะมาในรุปแบบที่ประชาชนโห่ร้องดีใจ เฉลิมฉลองการเกิดขึ้นของมันโดยไม่รู้สึกว่า เสรีภาพในการจัดการด้านอาหารสิ้นสุดลงแล้ว ในทางหนึ่ง มันอาจดูสวยงามไร้ที่ติ ช่วยลดการฆ่าสัตว์ ลดการปล่อยก๊าซเรือนกระจก และให้โปรตีนสะอาดแก่คนจำนวนมาก
แต่อีกทางหนึ่ง มันคือการรวมศูนย์อำนาจด้านอาหารไว้ในมือบริษัทยักษ์ใหญ่ ที่สามารถตั้งราคาตามใจ และควบคุมทุกขั้นตอนตั้งแต่ฟาร์ม (ในหลอดทดลอง) ถึงโต๊ะอาหารของเรา
เกษตรกรจะหมดบทบาท เพราะไม่มีใครต้องเลี้ยงสัตว์อีก ผู้บริโภคจะหมดทางเลือก เพราะสูตรทุกอย่างถูกจดสิทธิบัตร สุดท้าย คนธรรมดาอย่างเราอาจ “มีเงินก็ยังไม่มีสิทธิ์ทำอาหารกินเอง”
ไม่มีใครในหมู่บ้านจะต้มแกงจากวัตถุดิบแล็บเหล่านี้ได้โดยไม่จ่ายค่าลิขสิทธิ์ ไม่มีใครปลูกหรือเพาะเนื้อได้เอง เพราะเขาถือสิทธิบัตร ไม่มีใครรู้ส่วนผสมที่แท้จริง เพราะมันคือ “ความลับทางการค้า”
หลายๆคนเริ่มคิดในใจว่า…นี่ไม่ใช่เรื่องเล็กอีกต่อไป เพราะนี่อาจไม่ใช่แค่เนื้อจากห้องแล็บ แต่ มันคือจุดเริ่มต้นของอนาคตของอาหารที่ไม่เป็นของประชาชนอีกต่อไป มันคือการเริ่มต้นของยุคที่มนุษย์จะไม่สามารถ “เข้าครัวของตัวเอง” ได้อีกต่อไป
ไหนๆเราตามมาถึงตอนนี้แล้ว เข้าหมวดที่ 2 ของอาหารอนาคตแล้ว เฮียไม่ได้บอกว่าเทคโนโลยีไม่ดีนะครับ เราตัดสินเดี๋ยวนี้ไม่ได้ แต่เรารู้เรื่องของมันได้
แต่โลกนี้เต็มไปด้วยคำว่า “ดีต่อโลก” ที่ซ่อนคำว่า “ดีต่อผู้ถือหุ้น” อยู่ข้างใน เราอาจจะกำลังก้าวสู่ยุคที่ “เนื้อไม่ได้ปลอดภัยขึ้น แต่ถูกควบคุมง่ายขึ้น” และประชาชนก็อาจกลายเป็นเพียง “ผู้ใช้บริการเนื้อ” ที่ไม่มีสิทธิ์แม้แต่จะรู้ว่าเนื้อในจานคืออะไรบ้างแน่
โลกอาหารในอนาคตไม่ได้ขึ้นกับว่าเราปลูกอะไร แต่ขึ้นกับว่า “ใครจดสิทธิบัตรก่อน” และเมื่อถึงวันนั้น เฮียแอบคิดว่า เราอาจไม่ได้เสียแค่ฟาร์มและครัว แต่เรากำลังเสีย “เสรีภาพในการกิน” ไปอย่างช้า ๆ ด้วยรอยยิ้มของนักลงทุนและเสียบปรบมือจาก "ใครบางคน"
ทุกวันนี้ใครนิยมไดเอทอะไร ภูมิใจในการดูแลสุขภาพยังไง ก็ทำไปเหอะครับ ขอเพียงว่า เส้นทางที่เดินอยู่นั้น สนับสนุนเกษตกร สนับสนุน local ให้แข็งแรง ทุกสังคมมีทั้งคนดีและคนไม่ดี เราค่อยๆ verify สนับสนุนคนดีๆ แต่ไม่ใช่ไปเดียจฉันท์ลงโทษคนไม่ดี เราเสริมความรู้ให้เขา พยายามโอบอุ้มพวกเขา ถ้าชีวิตดีขึ้น การออมเห็นผลขึ้น อาจทำให้ชีวิตทุกคนดีขึ้น
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 0c65eba8:4a08ef9a
2025-05-28 15:28:47
@ 0c65eba8:4a08ef9a
2025-05-28 15:28:47You’ve heard the word.
You’ve probably used it. Maybe even hurled it at someone in a moment of pain. "Narcissist."
It lands like a curse.
And in today’s culture, it is one.
Not because it’s accurate.
But because it’s easy and packs a gut punch.
We blame narcissism for everything now. Every breakup. Every betrayal. Every moment someone’s ego gets in the way of our feelings.
Girls love to call their boyfriends narcissists when they feel neglected or controlled. Men love to call shallow women narcissists when they note the slightest vanity.
Friends turn on each other. Parents diagnose their children. Exes declare psychological war.
It’s become the pop-psych version of original sin.
But here’s the problem: the way we use this word is no longer grounded in clarity, science, or truth. It’s grounded in resentment.
And resentment is not a tool for diagnosis. It’s a weapon.
The Real Problem: Personality Dysfunction Is Rising
We are living in an era of personality dysfunction.
People hurt each other. They sabotage relationships, abandon their children, manipulate their spouses, destroy trust, and call it “self-care.”
Something is wrong. Deeply wrong.
We’ve studied it. Therapists, researchers, and social commentators have all tried to map it out.
And to be fair, some of those efforts have succeeded.
Certain patterns of personality dysfunction can be measured, tracked, and treated. When a trait can be operationalized, when we can define it clearly, measure it consistently, and test interventions reliably, it becomes useful. It becomes a tool for healing, not a weapon of blame.
For a psychological label to be scientifically sound, it must meet these criteria:
Antisocial Personality Disorder, for example, has clear markers: chronic dishonesty, demonstrated disregard for others, lack of remorse, impulsive behavior. It can be identified across time and context, and most importantly, it responds to specific interventions.
But narcissism?
The term doesn’t hold up.
It fails the tests of clarity, reliability, and usefulness. One therapist might see narcissism in a man who talks proudly about his accomplishments; another sees the same behavior as sharing leadership wisdom. One woman calls her ex a narcissist because he set boundaries; another praises those same traits in her new husband. A father who struggles to express affection gets pathologized as narcissistic by one adult child, and quietly respected for his restraint by another.
The label lacks tether. It’s not anchored to cause, behavior, or result.
It floats. It morphs. It reflects less about the person being described, and more about the insecurity or pain of the one using it.
And in trying to describe everything, it ends up describing nothing.
That’s not psychology. It’s projection.
We turned “narcissist” into a slur, a cudgel we swing at anyone who disagrees with us, makes us uncomfortable, or dares to outshine us. It’s no longer more useful than simply saying "man bad."
What Does "Narcissist" Even Mean?
So what does “narcissist” mean today?
Whatever the accuser wants it to mean.
Sometimes it means someone is confident. Other times, ambitious. Or assertive. Or charismatic. Or proud. Or selfish. Or charming. Or controlling. Or emotionally abusive. And sometimes, it simply means the other person didn’t agree with the accuser.
The list doesn’t end, because there is no clear definition.
When you call someone a narcissist, are you naming a trait? Or expressing your own pain? Or just reacting to how their ego made you feel?
Are you labeling a pattern of manipulation? Or just someone who knows they’re good at what they do? Or someone who’s willing to set a boundary that you don’t like?
We don’t know. And that’s the problem.
Side note: in my experience, true manipulators are the first to accuse others of manipulation. It’s a preemptive strike, a decoy. They believe if they say it first, it shields them from being exposed.
The same thing happens with the word narcissist.
Narcissism Doesn’t Survive Scientific Scrutiny
Before we go further, let’s look at what the DSM-5 actually says about Narcissistic Personality Disorder. These are the official diagnostic traits, and how each one collapses under scrutiny when we try to apply it with clarity, truth, and reciprocity.
What we find is simple: for every trait listed, we already have a better, more operational term. One that doesn’t blur the line between pathology and personality. One that can be observed, measured, and acted on.
But don’t just take my word for it, let’s examine the clinical roots and see how shallow they really are.
Here’s what that disambiguation looks like:
Every trait here has a clearer name or description. Every clearer name leads to a clearer solution. Calling it narcissism blurs the edges. Disambiguation sharpens them.
And one special note about empathy, since this trait is one of the most weaponized, it deserves a direct clarification. Most people don’t understand what empathy really is, let alone how it works in the real world:
When most people say "you lack empathy," what they really mean is "you didn’t agree with me or do what I wanted." But empathy is not blind compliance. It’s a limited, precious resource. It takes energy. It takes time. And it must be rationed.
We cannot, and should not, extend unlimited empathy to those outside our Circle of Care. Empathy isn’t just a warm feeling. It’s a costly act. It asks you to notice someone else’s pain, feel it, and then respond, often at the expense of your own time, energy, or resources.
So we ration it. We prioritize it. We give it to those we are responsible for, to those we love, to those who have earned our care. That’s not cruelty. That’s stewardship.
The real danger is when manipulators demand empathy as proof of virtue. “If you cared, you’d give me what I want.” But empathy is not submission. It is not forced agreement. It is not the abandonment of your own boundaries. Saying no with a clear heart is not a failure of empathy, it’s the mark of someone who knows where their responsibility ends, and where someone else’s manipulation begins. That’s wisdom. Because your emotional bandwidth, like every other resource, must be spent where it creates the most good.
Because of its vague boundaries, once someone learns the word “narcissist,” they start seeing it everywhere.
Every ex becomes one. Every bad boss. Every failed friendship. Every powerful man or beautiful woman who made them feel small. And soon, it doesn’t stop at relationships. It creeps into how they explain everything, from the decline of civilization to the state of politics and culture. Narcissism becomes the catch-all villain behind every social ill. Because the word is so vague, it always fits. But at that scale, the diagnosis becomes dangerous. It blocks our ability to understand people’s real motivations, incentives, fears, and goals. It replaces thought with accusation, and understanding with outrage.
They see narcissists everywhere, but they don’t ask if they’re the ones attracting toxic people, or if they’ve simply trained their lens to label every disappointment as abuse and every disagreement as pathology.
It’s projection disguised as insight.
And when you weaponize a label like that, you’re not analyzing behavior. You’re avoiding self-examination.
Three Core Arguments That Undermine the Narcissism Narrative
Now that we’ve seen how narcissism fails the scientific and diagnostic test, let’s break down the broader cultural problem. These are the three key reasons the term “narcissist” no longer serves us, and often does more harm than good.
1. "Narcissist" Doesn’t Mean Anything Specific, It Just Means You Don’t Like Them
The term is used as a junk drawer for traits people don’t want to deal with:
-
Confidence
-
Pride
-
Assertiveness
-
Visibility
But these traits, when tempered by maturity and ethics, are not only acceptable, they’re necessary.
-
Confidence inspires.
-
Pride in your work drives excellence.
-
Assertiveness enables leadership.
-
Visibility allows others to follow.
So when do these traits become toxic?
They don’t.
Not by themselves.
They only become dangerous when fused with things like entitlement, cruelty, dishonesty, or impulsiveness. And if those are the real problems, we should name them precisely.
Anything else is diagnostic laziness.
2. It’s Become a Weapon, Not a Diagnosis
Once upon a time, “narcissist” was treated as if it referred to a diagnosable condition. There was at least an attempt to define it scientifically and limit its use. But today, it's no longer grounded in discipline or diagnosis. It’s a social cudgel, vague, emotional, and endlessly adaptable to whatever someone wants to condemn.
People use it to:
-
Discredit others
-
Silence dissent
-
Justify moral superiority
And worst of all: you can’t defend yourself against it. The accusation is the evidence.
Try denying it. Say, "No, I don’t think highly of myself," and you disqualify yourself from being taken seriously. You’re signaling weakness, not humility. Especially for men, especially for leaders, denying your own value is social suicide.
Try asserting the truth instead. Say, "I’m not a narcissist, I’m just good at what I do." And that will be taken as proof of the accusation.
This trap doesn’t correct behavior. It crushes identity. It teaches the confident to shrink, the capable to self-doubt, and the virtuous to pretend they’re ordinary. Over time, especially in young men, this leads to collapse, of initiative, of drive, of self-respect.
We shouldn’t be pathologizing strong egos. We should be cultivating them, anchored in virtue, tethered to reality, and grounded in service. Confidence that comes from earned excellence isn’t narcissism. It’s maturity.
It’s time to stop punishing people for knowing who they are.
This isn’t psychology. It’s witch-burning.
3. We Already Have Better Words
If someone is manipulative, call them that. If someone lacks empathy, say so. If they’re arrogant, dishonest, or abusive, we already have words for those things.
Using “narcissist” to describe all of them at once is like checking your heart rate to diagnose a broken leg.
Vague terms destroy discernment.
Precise terms help us solve problems.
What About the People We’re Tearing Down?
Now here’s the part they don’t tell you:
Some of the people who get labeled “narcissist” aren’t dysfunctional at all.
They’re just better.
Better than average. Smarter. Stronger. More creative. More aware of their power. And because of that, they’re seen as dangerous.
So we drag them back down.
Like crabs in a bucket.
We’d rather insult than ascend.
We’d rather pathologize excellence than rise to meet it.
This is cultural suicide.
A Better Way to Protect Yourself
Here’s the better path forward:
-
Stop using “narcissist” as a placeholder for pain, disagreement, or vague discomfort.
-
Name the real traits, good or bad.
-
Learn how manipulation works and how to defend against it.
If you’ve ever been manipulated, gaslit, or emotionally preyed on, there’s a better way to understand it than these pop-psych terms.
That’s why I wrote this:
Become Immune to Manipulation: They Are Manipulating You and How to Resist It
It’s a guide to help you:
-
Detect manipulation in real time
-
Understand the tools manipulators use
-
Build defenses rooted in clarity, strength, and Natural Law
It’s short. It’s blunt. And it will change how you see people.
Read it. Share it. Live by it.
Because if you want to protect yourself from emotional predators, you don’t need therapy-speak.
You need a sword.
Retire the Label. Restore the Truth.
The truth is simple:
We don’t fix culture by inventing new labels. We fix it by restoring clarity, praising the good, correcting the harmful, and refusing to weaponize our language against truth.
So let’s stop using the narcissist slur.
And start seeing people for who they really are.
-
-
 @ 33baa074:3bb3a297
2025-05-28 07:50:06
@ 33baa074:3bb3a297
2025-05-28 07:50:06Soil moisture is a key factor that affects the structure and function of soil microbial communities. Here are some of the main aspects of how soil moisture affects microorganisms:
Affecting the Growth and Metabolism of Microorganisms Changes in soil moisture content directly affect the growth and metabolic activities of microorganisms. Under suitable moisture conditions, microorganisms are better able to carry out metabolic activities, thereby promoting the decomposition of soil organic matter and the transformation of nutrients. However, under extremely dry or overly wet conditions, the activity of microorganisms will be inhibited, resulting in a decline in soil functions.

Changing the Structure of Microbial Communities Changes in soil moisture conditions can lead to significant changes in the structure of microbial communities. For example, under drought conditions, the number of drought-tolerant microorganisms may increase to adapt to the water shortage environment. While under wet conditions, aerobic microorganisms may dominate. This change in community structure not only affects the soil's water retention capacity, but also other ecological functions of the soil.
Affecting the Stability of Soil Aggregates Soil aggregates are clumps formed by soil particles through physical, chemical and biological actions, and they have an important impact on the soil's water retention capacity. Soil microorganisms participate in the formation and stability of soil aggregates by secreting substances such as extracellular polymers. Appropriate soil moisture helps maintain the stability of soil aggregates, thereby improving the soil's water retention capacity. However, excessive moisture or drought may lead to the destruction of soil aggregates and reduce the soil's water retention capacity.
Regulating soil moisture dynamics Soil microorganisms can regulate the dynamic balance of soil moisture through their metabolic activities, such as decomposing organic matter and synthesizing exopolysaccharides. For example, some microorganisms can increase the water holding capacity of the soil by secreting exopolysaccharides, while others can release water by decomposing organic matter. These activities help maintain the stability of soil moisture and support plant growth.
Influencing the physical properties of soil Soil moisture can also indirectly affect the living environment of microorganisms by affecting the physical properties of the soil, such as pore structure and texture. Good soil pore structure is conducive to the penetration and storage of water, and also provides a suitable living space for microorganisms. Soil texture is closely related to the stability of aggregates. Sandy soils have poor aggregate stability and weak water retention capacity; while clay soils have good aggregate stability and strong water retention capacity.
In summary, soil moisture has many effects on microorganisms, including affecting the growth and metabolism of microorganisms, changing the structure of microbial communities, affecting the stability of soil aggregates, regulating soil moisture dynamics, and affecting the physical properties of soil. Therefore, maintaining suitable soil moisture conditions is of great significance for protecting the diversity and function of soil microbial communities and improving the water retention capacity of soil.
-
 @ 33baa074:3bb3a297
2025-05-28 07:27:02
@ 33baa074:3bb3a297
2025-05-28 07:27:02Distilled water has a wide range of applications in the medical field, mainly including the following aspects: Preparation of injection water Distilled water is an indispensable agent in medical institutions, used for the preparation of drugs, injection and washing of instruments, etc. In the medical process, sterile injection water is needed to flush wounds, prepare drugs, etc. The distilled water machine can ensure the purity of water and prevent microorganisms and harmful substances in the water from causing harm to patients.
Surgical wound flushing In breast cancer surgery, warm distilled water is used to flush surgical wounds. This practice helps to clean the wound, remove possible residual tumor cells, and use hypnotic effect to make tumor cells absorb water, swell, rupture, and necrotic, thereby preventing tumors from growing in the wound.
Cleaning and disinfection Distilled water has a certain disinfection and sterilization effect. It can be used to clean the skin, help eliminate bacteria on the skin surface, and is beneficial to the health of the skin. In addition, distilled water can also be used to clean and disinfect medical equipment to ensure the hygiene and safety of the medical environment.
Laboratory use In medical-related laboratories, distilled water is used to prepare experimental solutions, wash utensils and experimental instruments. These applications ensure the accuracy of experimental results while maintaining the sterile environment of the laboratory.
Moisturizing and Beauty Although not directly used in medical applications, distilled water is also used in skin care. It can be used as a basic moisturizer to help improve the symptoms of dry skin. In the field of medical beauty, distilled water is sometimes used for facial compresses to achieve calming, cooling, and swelling effects.
In summary, the application of distilled water in the medical field is multifaceted, from basic injection water preparation to complex surgical assistance to daily skin care, it has played an important role.
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ b7274d28:c99628cb
2025-05-28 01:11:43
@ b7274d28:c99628cb
2025-05-28 01:11:43In this second installment of The Android Elite Setup tutorial series, we will cover installing the nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8 on your #Android device and browsing for apps you may be interested in trying out.
Since the #Zapstore is a direct competitor to the Google Play Store, you're not going to be able to find and install it from there like you may be used to with other apps. Instead, you will need to install it directly from the developer's GitHub page. This is not a complicated process, but it is outside the normal flow of searching on the Play Store, tapping install, and you're done.
Installation
From any web browser on your Android phone, navigate to the Zapstore GitHub Releases page and the most recent version will be listed at the top of the page. The .apk file for you to download and install will be listed in the "Assets."
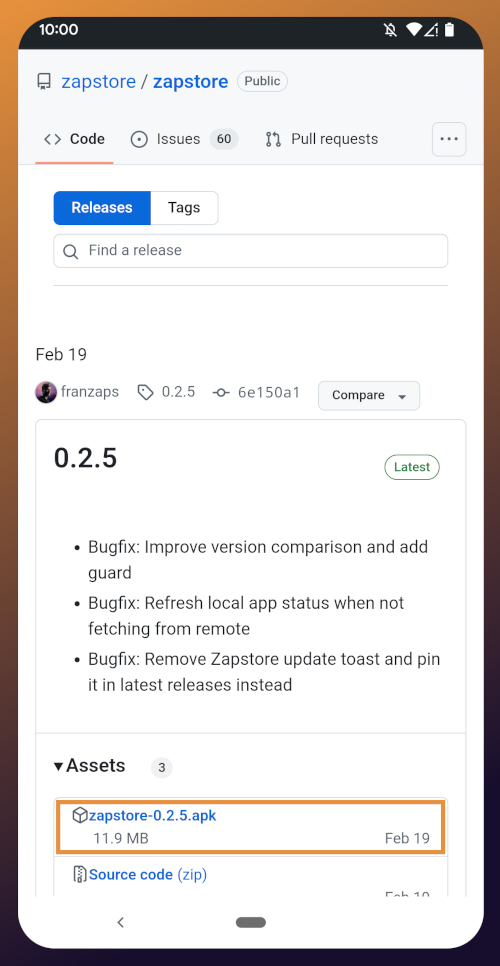
Tap the .apk to download it, and you should get a notification when the download has completed, with a prompt to open the file.
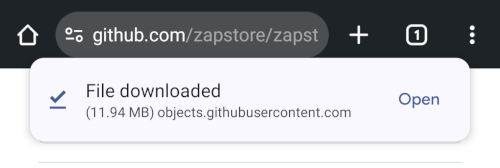
You will likely be presented with a prompt warning you that your phone currently isn't allowed to install applications from "unknown sources." Anywhere other than the Play Store is considered an "unknown source" by default. However, you can manually allow installation from unknown sources in the settings, which the prompt gives you the option to do.
In the settings page that opens, toggle it to allow installation from this source, and you should be prompted to install the application. If you aren't, simply go to your web browser's downloads and tap on the .apk file again, or go into your file browser app and you should find the .apk in your Downloads folder.
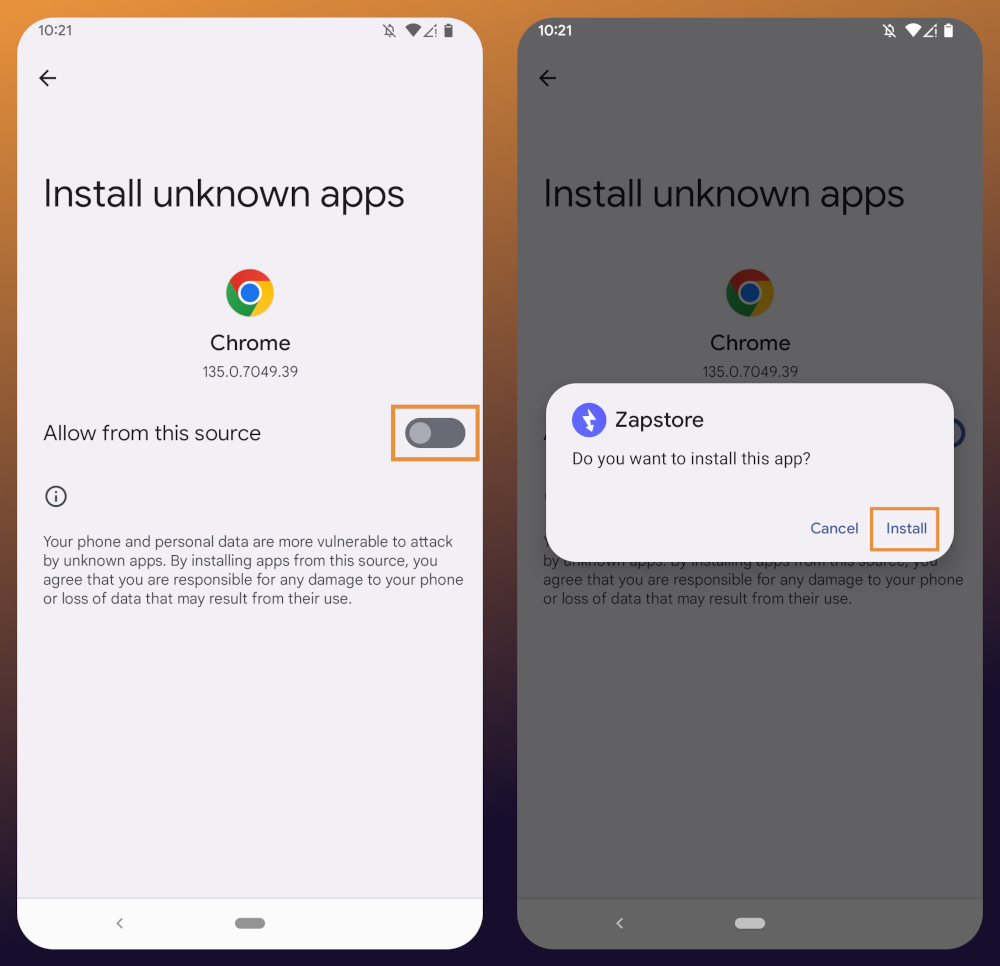
If the application doesn't open automatically after install, you will find it in your app drawer.
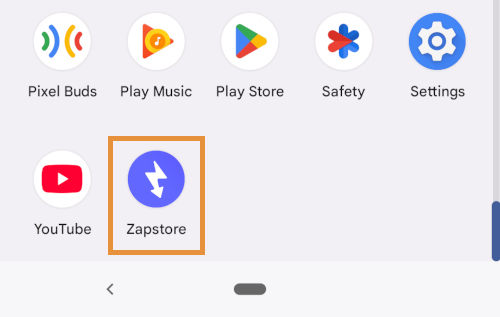
Home Page
Right at the top of the home page in the Zapstore is the search bar. You can use it to find a specific app you know is available in the Zapstore.
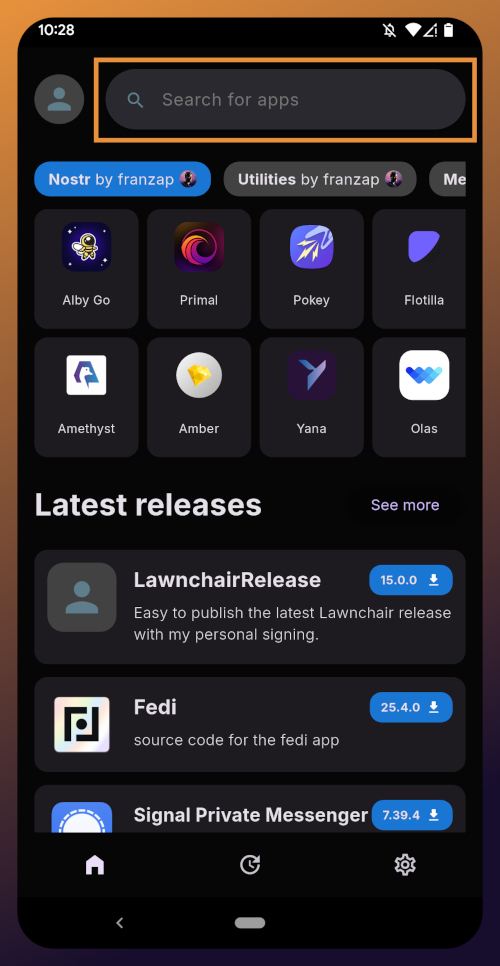
There are quite a lot of open source apps available, and more being added all the time. Most are added by the Zapstore developer, nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9, but some are added by the app developers themselves, especially Nostr apps. All of the applications we will be installing through the Zapstore have been added by their developers and are cryptographically signed, so you know that what you download is what the developer actually released.
The next section is for app discovery. There are curated app collections to peruse for ideas about what you may want to install. As you can see, all of the other apps we will be installing are listed in nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9's "Nostr" collection.
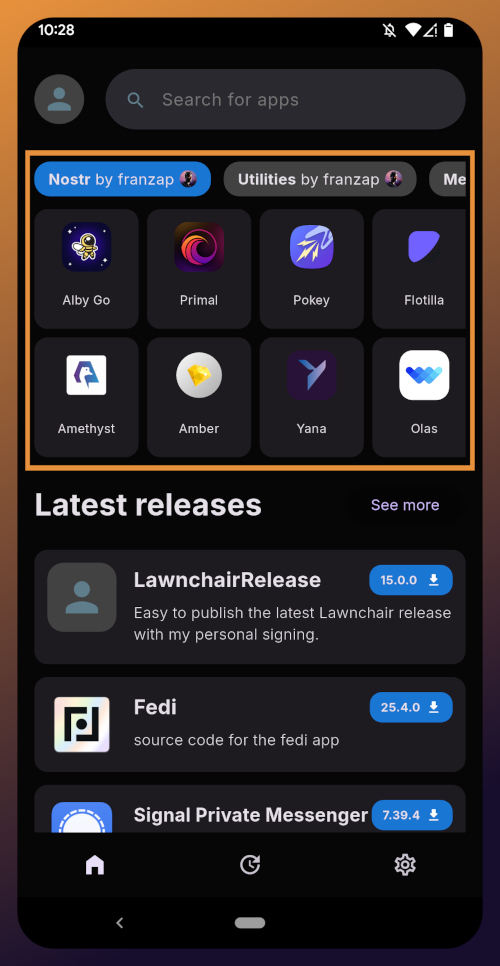
In future releases of the Zapstore, users will be able to create their own app collections.
The last section of the home page is a chronological list of the latest releases. This includes both new apps added to the Zapstore and recently updated apps. The list of recent releases on its own can be a great resource for discovering apps you may not have heard of before.
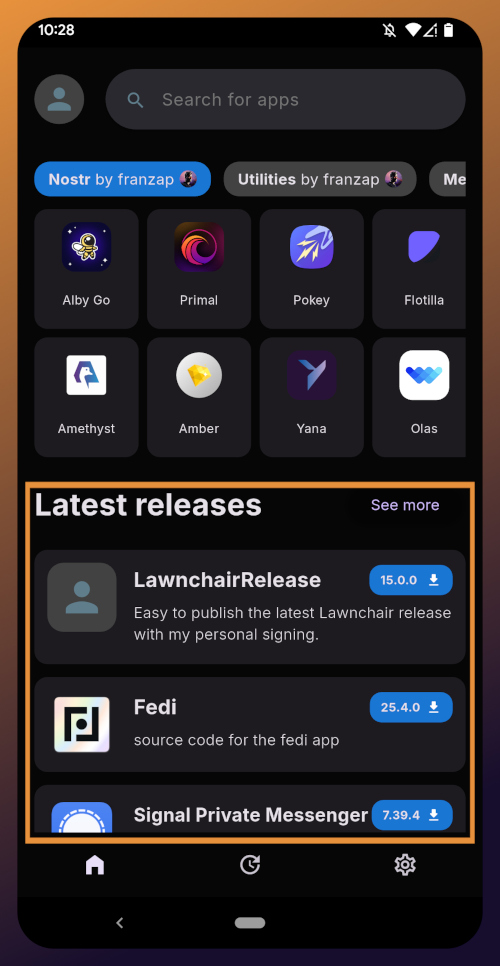
Installed Apps
The next page of the app, accessed by the icon in the bottom-center of the screen that looks like a clock with an arrow circling it, shows all apps you have installed that are available in the Zapstore. It's also where you will find apps you have previously installed that are ready to be updated. This page is pretty sparse on my test profile, since I only have the Zapstore itself installed, so here is a look at it on my main profile:
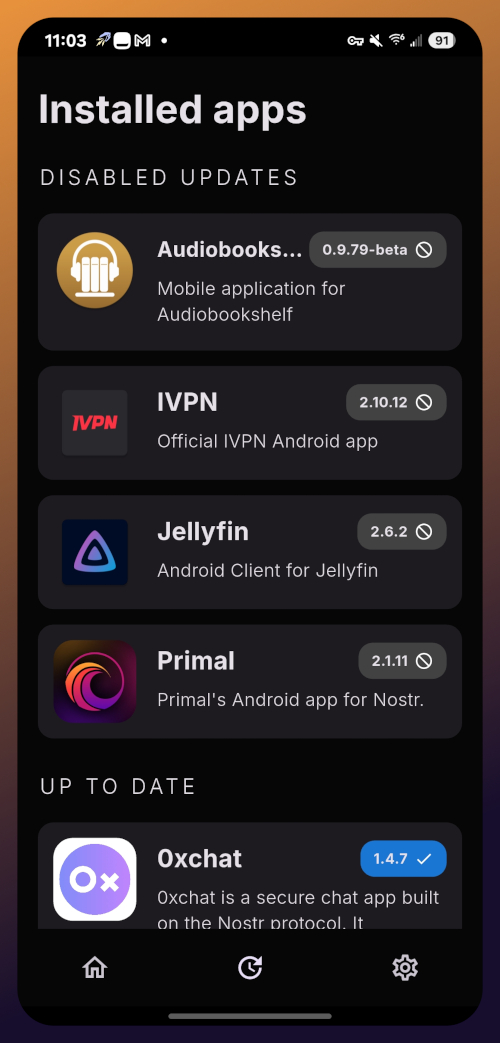
The "Disabled Apps" at the top are usually applications that were installed via the Play Store or some other means, but are also available in the Zapstore. You may be surprised to see that some of the apps you already have installed on your device are also available on the Zapstore. However, to manage their updates though the Zapstore, you would need to uninstall the app and reinstall it from the Zapstore instead. I only recommend doing this for applications that are added to the Zapstore by their developers, or you may encounter a significant delay between a new update being released for the app and when that update is available on the Zapstore.
Tap on one of your apps in the list to see whether the app is added by the developer, or by the Zapstore. This takes you to the application's page, and you may see a warning at the top if the app was not installed through the Zapstore.
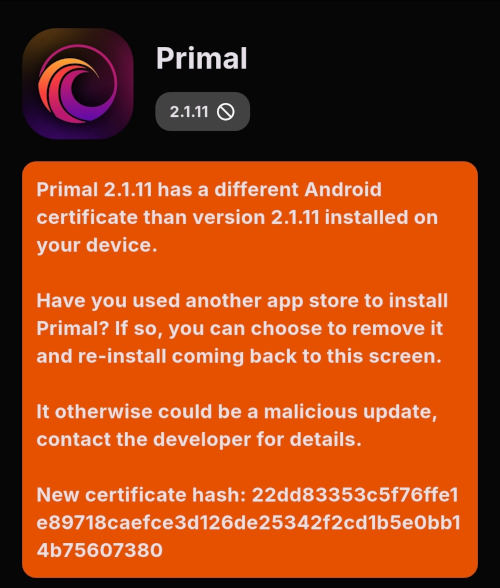
Scroll down the page a bit and you will see who signed the release that is available on the Zapstore.
In the case of Primal, even though the developer is on Nostr, they are not signing their own releases to the Zapstore yet. This means there will likely be a delay between Primal releasing an update and that update being available on the Zapstore.
Settings
The last page of the app is the settings page, found by tapping the cog at the bottom right.
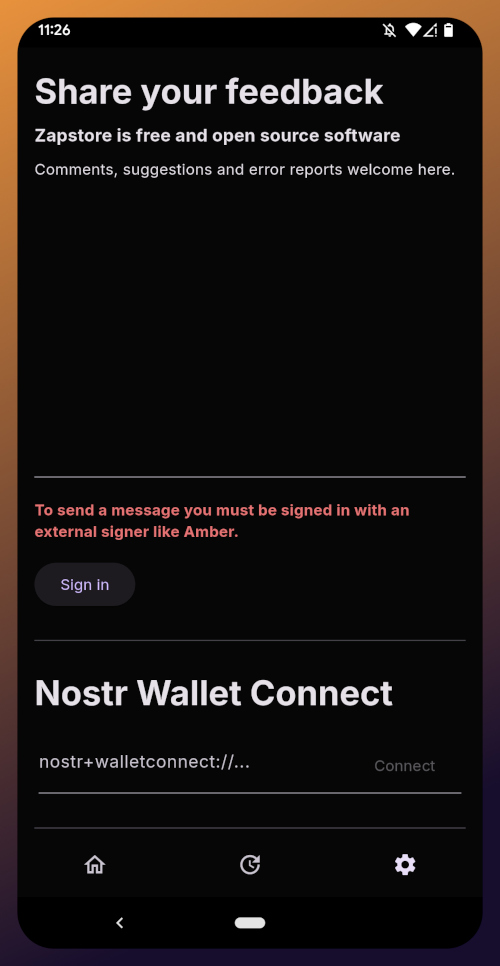
Here you can send the Zapstore developer feedback directly (if you are logged in), connect a Lightning wallet using Nostr Wallet Connect, delete your local cache, and view some system information.
We will be adding a connection to our nostr:npub1h2qfjpnxau9k7ja9qkf50043xfpfy8j5v60xsqryef64y44puwnq28w8ch wallet in part 5 of this tutorial series.
For the time being, we are all set with the Zapstore and ready for the next stage of our journey.
Continue to Part 3: Amber Signer. Nostr link: nostr:naddr1qqxnzde5xuengdeexcmnvv3eqgstwf6d9r37nqalwgxmfd9p9gclt3l0yc3jp5zuyhkfqjy6extz3jcrqsqqqa28qy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qg6waehxw309aex2mrp0yhxyunfva58gcn0d36zumn9wss80nug
-
 @ fd78c37f:a0ec0833
2025-04-01 11:49:06
@ fd78c37f:a0ec0833
2025-04-01 11:49:06In this edition, we invited Keypleb, the founder of Bitcoin Indonesia, to share how he built the Bitcoin community in Indonesia, overcoming challenges like member turnover and venue selection, while driving the adoption and growth of Bitcoin.
YakiHonne: Welcome, Keypleb. Before we begin, let me briefly introduce YakiHonne. YakiHonne is a decentralized media client built on Nostr—a protocol designed to empower freedom of speech through technology. It enables creators to own their voices and assets while offering innovative tools like smart widgets, verified notes, and support for long-form content. We focus on free speech and free media by user privacy and data to be protected. So before starting the interview, I'd like to hear about yourself and your community.
Keypleb:My name is Keypleb, though it’s a pseudonym—a name I use to respect privacy. I'm a co-founder of Bitcoin Indonesia, Bitcoin House Bali, and Code Orange, a new developer school we launched at a conference just a few days ago. We focus on driving adoption through meetups, hackathons, and technical workshops. I'll dive into more details later, but that's a brief overview. I'm based in Bali now, though I travel a lot and consider myself quite nomadic. Great to be here.
YakiHonne: What sparked your interest in Bitcoin and what motivated you to create a community on Bitcoin?
Keypleb:I first got interested in Bitcoin because it solved a specific problem. At the time, I didn’t know exactly what the solution was, but the problem was that I couldn’t afford a home. Back in 2019, I was living in London, and a two-bedroom apartment was £600,000, which was insanely expensive. First-time buyers like myself simply couldn’t afford it. Why was it so expensive? Why was buying a house so hard? During the COVID lockdown, I had more time on my hands and started listening to Michael Saylor on a Bitcoin podcast, where he talked about how the system is rigged, and that’s why people work hard but still can’t afford a house. That really resonated with me. So I started looking for a community, but unfortunately, there wasn’t one.. Keypleb:After moving to Bali, I attended a lot of crypto meetups, especially scammy altcoin ones, thinking, “There has to be a solution.” But none of them resonated with me. There was no sense of freedom, and no real discussion about inflation resistance. I remembered a podcast from Dea Reskita, an Indonesian host who’s pretty well-known online. I reached out to her and said, “ you’ve got to help me. I’m surrounded by all these shitcoiners, and I can’t take it anymore. I need a real community. Is anything happening?” She replied, “Yes, something is happening. We should restart these meetups next month.” And that’s how it all began. Keypleb:There’s also another story about how we started Bitcoin House and how Bitcoin in Asia came to be, but maybe I’ll save that for later. Anyway, the spark of interest came from Bitcoin solving a real problem, and my drive to keep going came from the lack of quality meetups. Now, we’ve hosted 31 meetups, launched Bitcoin House and Code Orange, and the movement is growing rapidly.

YakiHonne: That’s such an amazing story—going from being on the brink of homelessness to creating something so impactful, and keeping it running every day, bringing new people into the journey. It’s truly inspiring. I’m curious about how the community started. How did you manage to attract members and build a strong community? What challenges did you face along the way?
Keypleb:It all started with our first meetup at the end of 2022, which was two and a half years ago now. At that time, we sent out an email to a group from a previous database, and the first meetup had around 20 people, which was a good start. However, problems quickly arose as people started dropping off, and the community lacked retention. In Bali, people come and go, usually staying for no more than two months, leading to a lack of long-term participation. This became one of our challenges: how to attract more people and, more importantly, get the same people to keep coming back. While I've been coming back for two and a half years, not everyone is able to return as often, and that has been a real challenge. Keypleb:Actually, I should also mention how I met my co-founders—Marius, Diana, and Dimas. We met at the 2023 Indonesia Bitcoin Conference. As time went on, we kept hosting meetups and had a lot of fun each time, though the locations kept changing. One of the initial challenges was that we didn't realize the importance of having a fixed meetup location. We changed venues several times before we realized that having a consistent location is crucial. If anyone wants to run a meetup, it's best to always choose a fixed location. We learned this through trial and error, but now it's no longer an issue. Keypleb:Since the conference, my co-founders and I have been working together, consistently putting in the effort. This is why our community has grown so large—so far, we are hosting 31 monthly meetups, 6 of which are in Bali. This means there is a bitcoin meetup almost every day on a regular basis. We've also established Bitcoin House Bali, a physical space, and the movement is growing rapidly. Without this movement, the region would face many challenges, including inflation and heavy censorship. It all started from just one meetup.
 YakiHonne: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now?
YakiHonne: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now?Keypleb:First, one very important piece of advice is to ensure that every meetup is held at the same location regularly. We realized this challenge through trial and error. To help others who are interested, we’ve published our meetup guide on GitHub, where everyone can check it out. For example, meetups should be held regularly, ideally once a month, or even once a week. In Chiang Mai, the Bitcoin meetup starts every Thursday at 7 PM, and everyone knows the time and location, making it easy to join without having to look up the next meetup. Keypleb:Additionally, our meetup structure is very simple. First, we do a round of introductions where everyone shares their name, where they’re from, and what Bitcoin means to them. This usually takes about 15 minutes. Then, we discuss three main questions: First, why do we need Bitcoin? The discussion typically focuses on two main issues Bitcoin addresses: inflation and censorship;Secondly, how to buy Bitcoin? We usually ask who wants to buy some Bitcoin, and then we do a small purchase together and conduct a P2P trade to demonstrate how easy it is to buy Bitcoin. Lastly, how to store Bitcoin? We introduce self-custody and show how to use hardware wallets (like Trezor), explaining the concept of the 12 words and private keys. Keypleb:The whole meetup usually wraps up in about an hour, after which people can continue socializing at Bitcoin House or wherever the meetup is taking place. In short, keeping the meetup simple and efficient, and ensuring a fixed location for each event, are key factors in building a successful community.
YakiHonne: What's the major approach? Is it more technical, or do you focus on non-technical aspects, or do you cover both?
Keypleb:Our approach includes both technical and non-technical content. Initially, our meetups were completely non-technical, just casual gatherings for people to socialize. Over time, however, we've evolved to incorporate more technical content. Keypleb:Out of the 31 monthly regular meetups we host, most of them have been non-technical, simply regular gatherings held at the same time and place according to our meetup guide. For example, we host the “Bitcoin for Beginners” meetup, which is designed for newcomers and takes place every second Friday of the month at 5 PM at the Bitcoin House Bali. This is entirely non-technical. Additionally, every Wednesday at Bitcoin House, we host the “My First Bitcoin” course. While the course touches on some technical aspects, such as seed phrases and backups, it’s still beginner-friendly and not too technical. The course runs for 10 weeks, and we plan to offer it in the local language at Bali University to help the local community better understand Bitcoin. Keypleb:On the other hand, we also offer highly technical content. We launched a new program called “Code Orange,” which is specifically designed for developers and programmers. We use the “Decoding Bitcoin” website, created by Jamal, which is a learning platform for developers. Many developer schools, like Code Orange, use this resource. Additionally, we host “Code Orange” meetups where we dive into the technical aspects of Bitcoin, such as how mining works and how to prevent single points of failure. Keypleb:We also organize technical workshops, such as “How to Defend Against a Five-Dollar Wrench Attack,” which is closely related to security. Recently, there have been some kidnapping incidents in Bali, and many people are concerned about their Bitcoin being stolen. To address this, we plan to hold a workshop on how to protect Bitcoin against such attacks. Additionally, we host hackathons and other high-tech events, and we just completed a very successful beginner-level hackathon. Keypleb:In summary, our community caters to everyone, from beginners to technical experts. For beginners, we offer easy-to-understand, non-technical content, while for experienced Bitcoiners, we provide in-depth technical material.
 YakiHonne: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved?
YakiHonne: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved?Keypleb:I have some additional advice. First, technical individuals can sign up for the “Decoding Bitcoin” course that starts on 18th March 2025 or join our “Code Orange” program and participate in the end-of-year hackathon. If they are technically proficient, this will be a great opportunity. “Decoding Bitcoin” is great for beginners, but it’s also useful for technical individuals. If someone is very skilled, they can start contributing code right away. If they find the course too easy, they can skip it and dive directly into more advanced projects. Additionally, Bitshala and Chaincode Labs offer advanced courses, which more technically advanced individuals can choose to pursue.
 Keypleb:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash.
Keypleb:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash.YakiHonne: I’d like to move on to the next question: How do you see Bitcoin communities evolving as technology progresses, particularly in areas like scalability, privacy, and adaptability to other systems? Keypleb:I believe the Bitcoin community will continue to evolve, and it has already made incredible progress. Two and a half years ago, we started alone in Bali, with just ourselves. We began in the official phase and have had numerous conversations throughout the year. For example, we are now starting a Bitcoin club at a university in Bali; we just need to find a passionate, driven “Bitcoin maximalist,” and the Bitcoin club will begin. Like what our friends did in Banyuwangi, Indonesia, these clubs could eventually evolve into Bitcoin houses.
Keypleb:Regarding privacy and scalability, the community is making strides. We’re big fans of Fedi, which builds on top of the Fedimint protocol and uses e-cash to scale Bitcoin while improving privacy. Fedi low fees and high privacy potential give Bitcoin great opportunities in this area. Keypleb:As for Bitcoin's compatibility with fiat systems, although Bitcoin payments are illegal in some countries like Indonesia, smart developers across Southeast Asia are working on legal solutions. For example, there's a website called Pleb QR that works in Thailand, allowing you to pay in fiat via the Lightning Network. Koral is another app specifically for Indonesia. These kinds of testing products already exist and are physically possible, but we’re just waiting on regulations. My influential friends are actively lobbying the government for adoption. Keypleb:In summary, privacy, scalability, and compatibility with fiat systems are all works in progress, and they will continue to evolve positively. There will be more meetups, more wallet downloads, and more adoption—there’s no doubt about that.
YakiHonne: You mentioned the concept of cross-country issues, so I have one last question: How is the government’s stance on Bitcoin? Is the political climate supportive or against Bitcoin? How do you see the government's approach to Bitcoin in your community or environment?
Keypleb:This reminds me of a person, Jeff Booth, who once said, “We are them, the government is made up of us.” In Indonesia, many politicians actually support Bitcoin, and many of them mine Bitcoin themselves. When money is involved, the incentive is strong, and politicians naturally like to make more money. As a result, Indonesia has a large Bitcoin mining scene. However, overall, the Indonesian government is against Bitcoin, as seen in their ban on Bitcoin payments. The 2011 currency law states that any currency other than the Indonesian Rupiah (IDR) cannot be used, and violators can face up to one year in prison or a fine. This means you cannot pay with US dollars, lira, euros, pesos or pounds. Keypleb:This shows that the government’s legal system is somewhat fragile. It’s understandable that the government is concerned about disruptive technologies like Bitcoin, especially with such a fragile fiat system. Indonesia has also seen many arrests. In 2016, Bank Indonesia issued a letter announcing a crackdown on cryptocurrency payments. Those involved in paying in Bitcoin had their funds seized, and the police cooperated in shutting down businesses accepting Bitcoin payments in the cities. While this isn't very friendly, it does highlight the fragility of the existing system. We also believe that a new executive order may be introduced in the future, similar to when President Roosevelt in 1933 ordered Americans to hand over all their gold with his Executive Order 6102. If it happened before, it could happen again. Keypleb:Therefore, we predict that Bitcoin custody could become a legal issue, which is one of the reasons we blur the faces of participants at every meetup. We need to protect the community from any potential risks. But overall, we remain optimistic. Despite the government ban, the ideology of Bitcoin is unstoppable, and its spread cannot be stopped. So, we are very optimistic about the future.
YakiHonne: I think almost every government around the world, even in Africa, faces similar issues with Bitcoin. Some governments might want Bitcoin but hesitate to openly accept it due to the fear of it undermining the traditional financial system, which, of course, could eventually happen. But hopefully, as the new generation comes into power, we'll see more Bitcoin-friendly governments. So, thank you so much for sharing your insights and advice. I really appreciate your time and the valuable input you've provided.
Keypleb:I'm really glad this conversation enlightened me. I enjoyed it a lot, and it made me reflect on how much work we're doing and how valuable it is. There are a lot of problems out there, with censorship being the biggest one, followed by inflation, which is also a major issue depending on the region. But Bitcoin is open, the community is growing, and people are fighting against censorship and internet shutdowns in places like Indonesia and beyond. The movement is definitely growing. So, I'm very happy to be here and have this chat. Thanks again.
Bitcoin Indonesia nostr: nostr:npub1y4qd2zhtn05gnsaaq5xfejzfk4a32638tx6gpp9g8k6e42g9d66qaxhcr3
Keypleb nostr: nostr:npub190trvg63e6tyqlwlj6lccqpftx76lckj25c006vwx3dzvdl88yxs2nyqdx
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ e6817453:b0ac3c39
2024-12-07 14:54:46
@ e6817453:b0ac3c39
2024-12-07 14:54:46Introduction: Personal Knowledge Graphs and Linked Data
We will explore the world of personal knowledge graphs and discuss how they can be used to model complex information structures. Personal knowledge graphs aren’t just abstract collections of nodes and edges—they encode meaningful relationships, contextualizing data in ways that enrich our understanding of it. While the core structure might be a directed graph, we layer semantic meaning on top, enabling nuanced connections between data points.
The origin of knowledge graphs is deeply tied to concepts from linked data and the semantic web, ideas that emerged to better link scattered pieces of information across the web. This approach created an infrastructure where data islands could connect — facilitating everything from more insightful AI to improved personal data management.
In this article, we will explore how these ideas have evolved into tools for modeling AI’s semantic memory and look at how knowledge graphs can serve as a flexible foundation for encoding rich data contexts. We’ll specifically discuss three major paradigms: RDF (Resource Description Framework), property graphs, and a third way of modeling entities as graphs of graphs. Let’s get started.
Intro to RDF
The Resource Description Framework (RDF) has been one of the fundamental standards for linked data and knowledge graphs. RDF allows data to be modeled as triples: subject, predicate, and object. Essentially, you can think of it as a structured way to describe relationships: “X has a Y called Z.” For instance, “Berlin has a population of 3.5 million.” This modeling approach is quite flexible because RDF uses unique identifiers — usually URIs — to point to data entities, making linking straightforward and coherent.
RDFS, or RDF Schema, extends RDF to provide a basic vocabulary to structure the data even more. This lets us describe not only individual nodes but also relationships among types of data entities, like defining a class hierarchy or setting properties. For example, you could say that “Berlin” is an instance of a “City” and that cities are types of “Geographical Entities.” This kind of organization helps establish semantic meaning within the graph.
RDF and Advanced Topics
Lists and Sets in RDF
RDF also provides tools to model more complex data structures such as lists and sets, enabling the grouping of nodes. This extension makes it easier to model more natural, human-like knowledge, for example, describing attributes of an entity that may have multiple values. By adding RDF Schema and OWL (Web Ontology Language), you gain even more expressive power — being able to define logical rules or even derive new relationships from existing data.
Graph of Graphs
A significant feature of RDF is the ability to form complex nested structures, often referred to as graphs of graphs. This allows you to create “named graphs,” essentially subgraphs that can be independently referenced. For example, you could create a named graph for a particular dataset describing Berlin and another for a different geographical area. Then, you could connect them, allowing for more modular and reusable knowledge modeling.
Property Graphs
While RDF provides a robust framework, it’s not always the easiest to work with due to its heavy reliance on linking everything explicitly. This is where property graphs come into play. Property graphs are less focused on linking everything through triples and allow more expressive properties directly within nodes and edges.
For example, instead of using triples to represent each detail, a property graph might let you store all properties about an entity (e.g., “Berlin”) directly in a single node. This makes property graphs more intuitive for many developers and engineers because they more closely resemble object-oriented structures: you have entities (nodes) that possess attributes (properties) and are connected to other entities through relationships (edges).
The significant benefit here is a condensed representation, which speeds up traversal and queries in some scenarios. However, this also introduces a trade-off: while property graphs are more straightforward to query and maintain, they lack some complex relationship modeling features RDF offers, particularly when connecting properties to each other.
Graph of Graphs and Subgraphs for Entity Modeling
A third approach — which takes elements from RDF and property graphs — involves modeling entities using subgraphs or nested graphs. In this model, each entity can be represented as a graph. This allows for a detailed and flexible description of attributes without exploding every detail into individual triples or lump them all together into properties.
For instance, consider a person entity with a complex employment history. Instead of representing every employment detail in one node (as in a property graph), or as several linked nodes (as in RDF), you can treat the employment history as a subgraph. This subgraph could then contain nodes for different jobs, each linked with specific properties and connections. This approach keeps the complexity where it belongs and provides better flexibility when new attributes or entities need to be added.
Hypergraphs and Metagraphs
When discussing more advanced forms of graphs, we encounter hypergraphs and metagraphs. These take the idea of relationships to a new level. A hypergraph allows an edge to connect more than two nodes, which is extremely useful when modeling scenarios where relationships aren’t just pairwise. For example, a “Project” could connect multiple “People,” “Resources,” and “Outcomes,” all in a single edge. This way, hypergraphs help in reducing the complexity of modeling high-order relationships.
Metagraphs, on the other hand, enable nodes and edges to themselves be represented as graphs. This is an extremely powerful feature when we consider the needs of artificial intelligence, as it allows for the modeling of relationships between relationships, an essential aspect for any system that needs to capture not just facts, but their interdependencies and contexts.
Balancing Structure and Properties
One of the recurring challenges when modeling knowledge is finding the balance between structure and properties. With RDF, you get high flexibility and standardization, but complexity can quickly escalate as you decompose everything into triples. Property graphs simplify the representation by using attributes but lose out on the depth of connection modeling. Meanwhile, the graph-of-graphs approach and hypergraphs offer advanced modeling capabilities at the cost of increased computational complexity.
So, how do you decide which model to use? It comes down to your use case. RDF and nested graphs are strong contenders if you need deep linkage and are working with highly variable data. For more straightforward, engineer-friendly modeling, property graphs shine. And when dealing with very complex multi-way relationships or meta-level knowledge, hypergraphs and metagraphs provide the necessary tools.
The key takeaway is that only some approaches are perfect. Instead, it’s all about the modeling goals: how do you want to query the graph, what relationships are meaningful, and how much complexity are you willing to manage?
Conclusion
Modeling AI semantic memory using knowledge graphs is a challenging but rewarding process. The different approaches — RDF, property graphs, and advanced graph modeling techniques like nested graphs and hypergraphs — each offer unique strengths and weaknesses. Whether you are building a personal knowledge graph or scaling up to AI that integrates multiple streams of linked data, it’s essential to understand the trade-offs each approach brings.
In the end, the choice of representation comes down to the nature of your data and your specific needs for querying and maintaining semantic relationships. The world of knowledge graphs is vast, with many tools and frameworks to explore. Stay connected and keep experimenting to find the balance that works for your projects.
-
 @ eb0157af:77ab6c55
2025-05-28 07:01:26
@ eb0157af:77ab6c55
2025-05-28 07:01:26Governor Abbott will have to decide whether to sign the bill establishing a bitcoin reserve for the state.
Texas could become the third U.S. state to set up a strategic bitcoin reserve, following the approval of Senate Bill 21 by the state House, with 101 votes in favor and 42 against.
Lee Bratcher, founder and president of the Texas Blockchain Council, expressed confidence that Governor Greg Abbott will sign the legislative measure. In an interview with The Block, Bratcher said:
“I’ve talked to the governor about this personally, and I think he wants to see Texas lead in this way.”
The bill is expected to reach the governor’s desk within a week or two, according to Bratcher’s projections. If signed, Texas would follow in the footsteps of New Hampshire and Arizona in creating a state-held bitcoin reserve.
Despite Texas ranking as the world’s eighth-largest economy — ahead of many nations — the initial approach to the reserve will be cautious. Bratcher estimates the starting investment will be in the “tens of millions of dollars,” an amount he describes as “modest” for an economy the size of Texas. The responsibility for operational decisions would fall to the state comptroller, who acts as an executive accountant in charge of managing and investing public funds.
“My sense is that it will be in the tens of millions of dollars, which, while it sounds significant, is a very modest amount, for a state the size of Texas.” explained the president of the Texas Blockchain Council.
The road to approval
According to Bratcher, the idea of creating a state bitcoin reserve dates back to 2022 and represents the culmination of years of work by the Texas Blockchain Council. The organization has worked closely with lawmakers who shared the vision of seeing the state accumulate the world’s leading cryptocurrency. Additionally, Texas has long been home to numerous bitcoin mining companies.
The post Texas one step away from a bitcoin reserve: only the governor’s signature is missing appeared first on Atlas21.
-
 @ b7274d28:c99628cb
2025-05-28 00:59:49
@ b7274d28:c99628cb
2025-05-28 00:59:49Your identity is important to you, right? While impersonation can be seen in some senses as a form of flattery, we all would prefer to be the only person capable of representing ourselves online, unless we intentionally delegate that privilege to someone else and maintain the ability to revoke it.
Amber does all of that for you in the context of #Nostr. It minimizes the possibility of your private key being compromized by acting as the only app with access to it, while all other Nostr apps send requests to Amber when they need something signed. This even allows you to give someone temporary authority to post as you without giving them your private key, and you retain the authority to revoke their permissions at any time.
nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 has provided Android users with an incredibly powerful tool in Amber, and he continues to improve its functionality and ease of use. Indeed, there is not currently a comparative app available for iOS users. For the time being, this superpower is exclusive to Android.
Installation
Open up the Zapstore app that you installed in the previous stage of this tutorial series.
Very likely, Amber will be listed in the app collection section of the home page. If it is not, just search for "Amber" in the search bar.
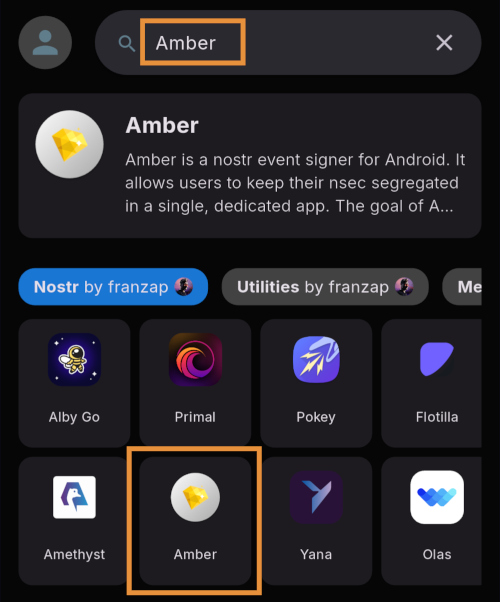
Opening the app's page in the Zapstore shows that the release is signed by the developer. You can also see who has added this app to one of their collections and who has supported this app with sats by zapping the release.
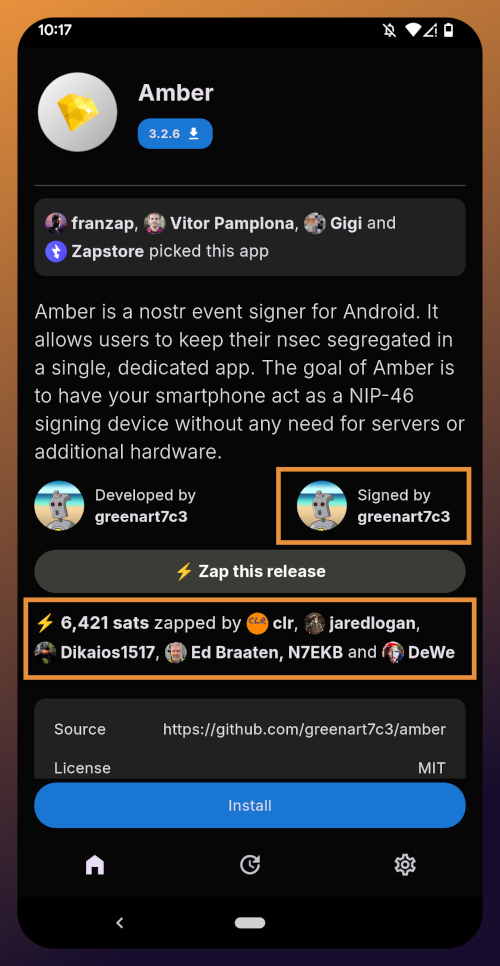
Tap "Install" and you will be prompted to confirm you are sure you want to install Amber.
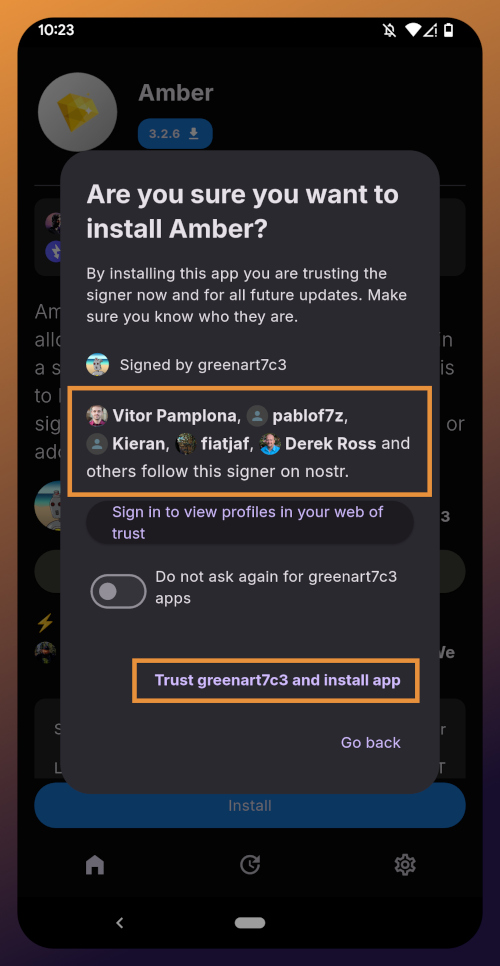
Helpfully, you are informed that several other users follow this developer on Nostr. If you have been on Nostr a while, you will likely recognize these gentlemen as other Nostr developers, one of them being the original creator of the protocol.
You can choose to never have Zapstore ask for confirmation again with apps developed by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, and since we have another of his apps to install later in this tutorial series, I recommend you toggle this on. Then tap on "Trust greenart7c3 and install app."
Just like when you installed the Zapstore from their GitHub, you will be prompted to allow the Zapstore to install apps, since Android considers it an "unknown source."
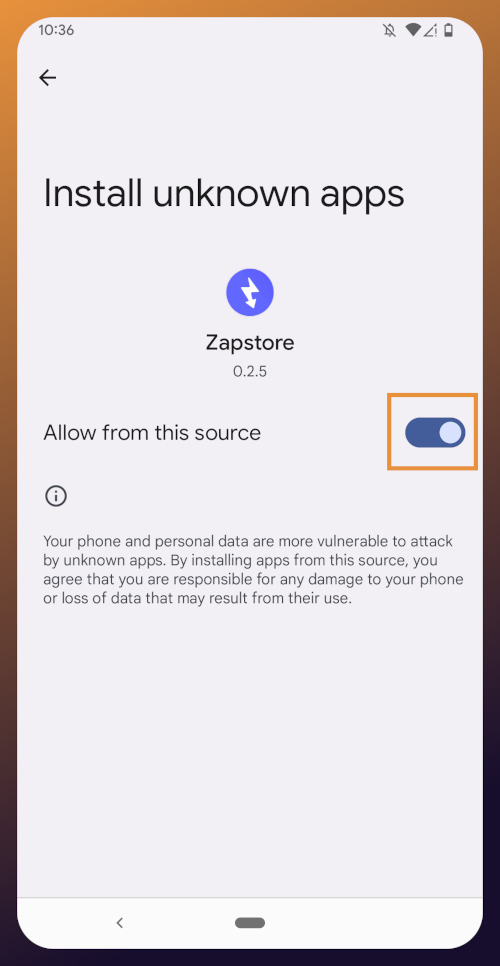
Once you toggle this on and use the back button to get back to the Zapstore, Amber will begin downloading and then present a prompt to install the app. Once installed, you will see a prompt that installation was a success and you can now open the app.
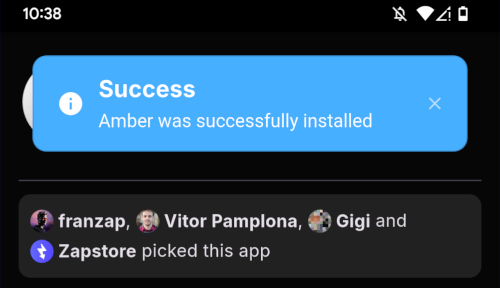
From here, how you proceed will depend on whether you need to set up a new Nostr identity or use Amber with an existing private key you already have set up. The next section will cover setting up a new Nostr identity with Amber. Skip to the section titled "Existing Nostrich" if you already have an nsec that you would like to use with Amber.
New Nostrich
Upon opening the application, you will be presented with the option to use an existing private key or create a new Nostr account. Nostr doesn't really have "accounts" in the traditional sense of the term. Accounts are a relic of permissioned systems. What you have on Nostr are keys, but Amber uses the "account" term because it is a more familiar concept, though it is technically inaccurate.
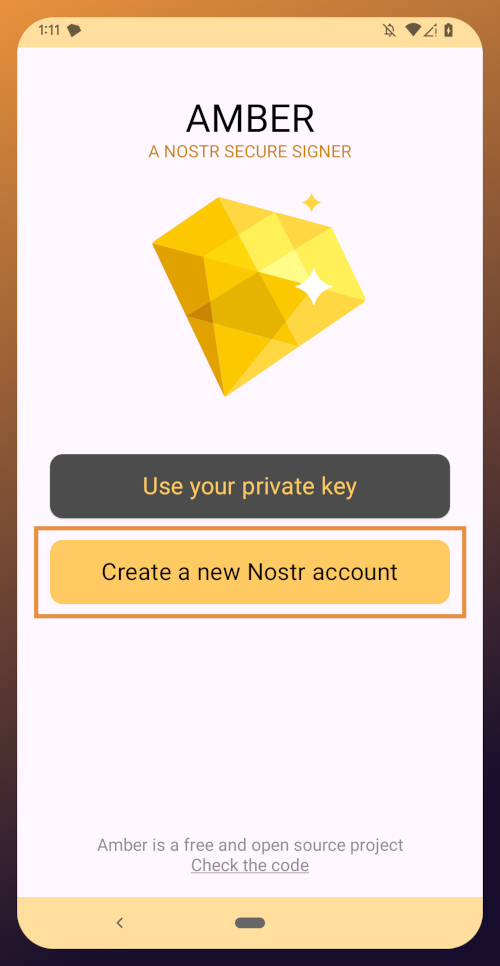
Choose "Create a new Nostr account" and you will be presented with a screen telling you that your Nostr account is ready. Yes, it was really that easy. No email, no real name, no date of birth, and no annoying capcha. Just "Create a new account" and you're done.
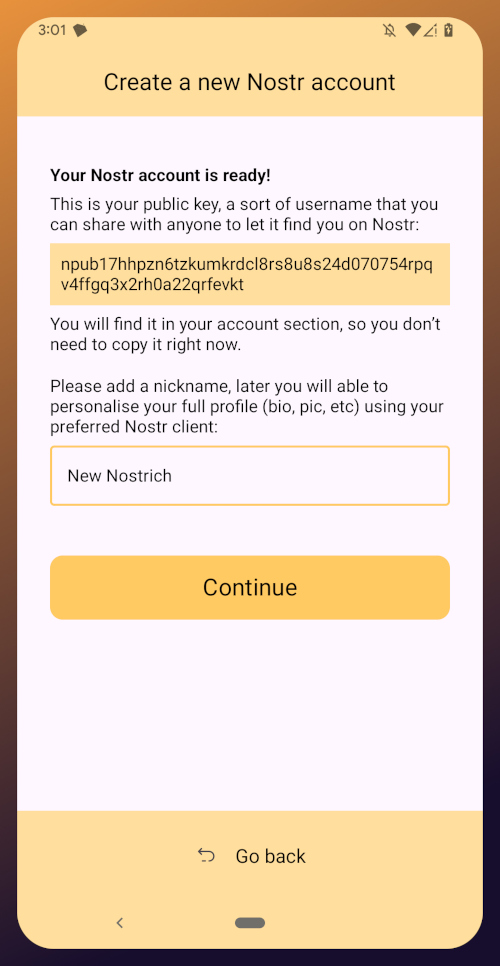
The app presents you with your public key. This is like an address that can be used to find your posts on Nostr. It is 100% unique to you, and no one else can post a note that lists this npub as the author, because they won't have the corresponding private key. You don't need to remember your npub, though. You'll be able to readily copy it from any Nostr app you use whenever you need it.
You will also be prompted to add a nickname. This is just for use within Amber, since you can set up multiple profiles within the app. You can use anything you want here, as it is just so you can tell which profile is which when switching between them in Amber.
Once you've set your nickname, tap on "Continue."
The next screen will ask you what Amber's default signing policy should be.
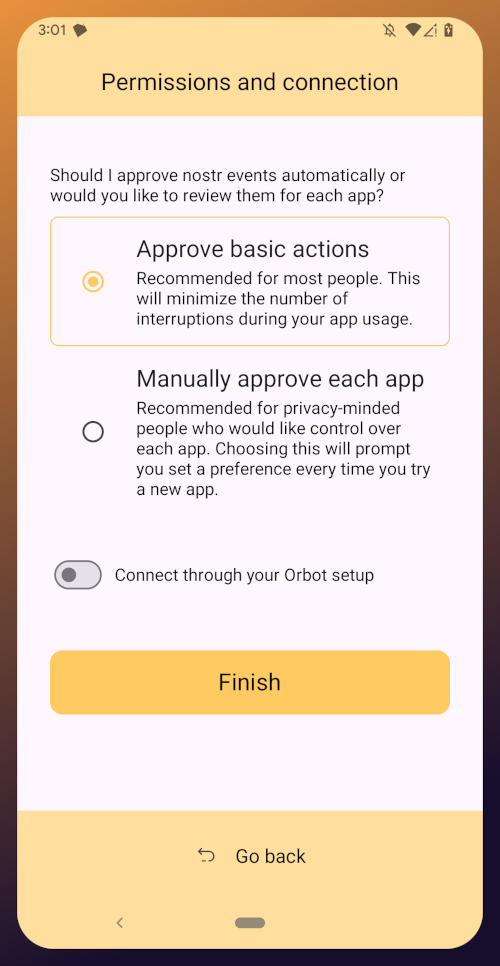
The default is to approve basic actions, referring to things that are common for Nostr clients to request a signature for, like following another user, liking a post, making a new post, or replying. If you are more concerned about what Amber might be signing for on your behalf, you can tell it to require manual approval for each app.
Once you've made your decision, tap "Finish." You will also be able to change this selection in the app settings at any time.
With this setup out of the way, you are now presented with the main "Applications" page of the app.
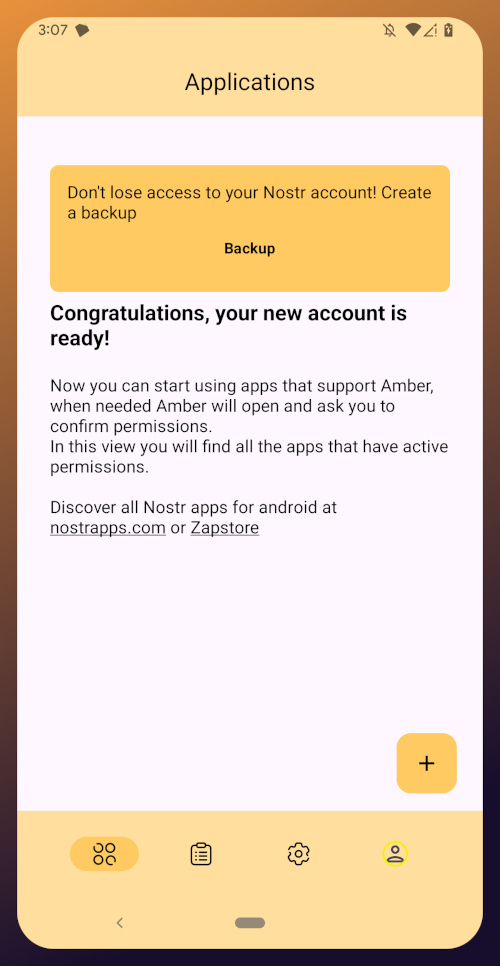
At the top, you have a notification encouraging you to create a backup. Let's get that taken care of now by tapping on the notification and skipping down to the heading titled "Backing Up Your Identity" in this tutorial.
Existing Nostrich
Upon opening the application, you will be presented with the option to use your private key or create a new Nostr account. Choose the former.
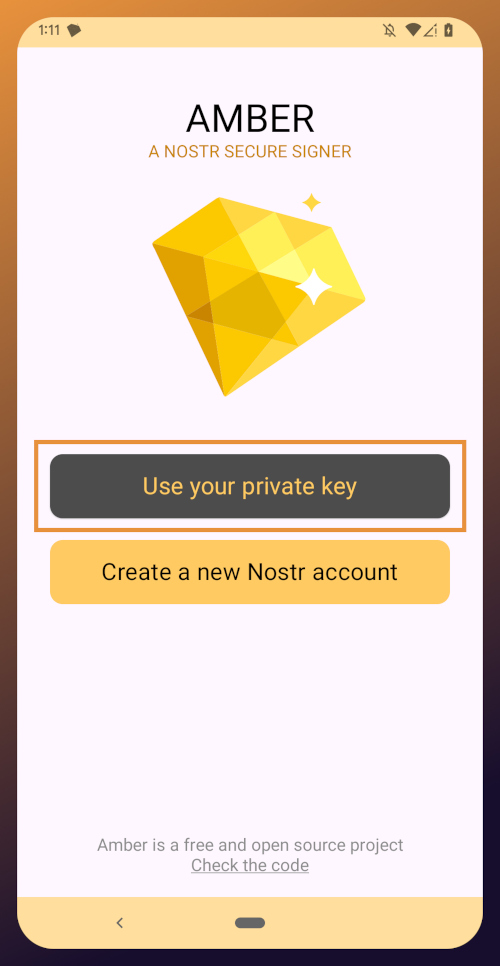
The next screen will require you to paste your private key.
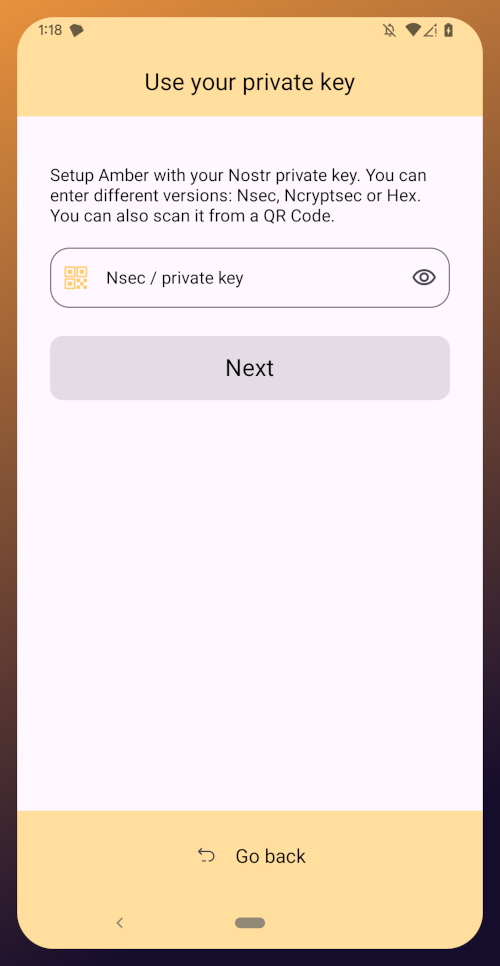
You will need to obtain this from whatever Nostr app you used to create your profile, or any other Nostr app that you pasted your nsec into in the past. Typically you can find it in the app settings and there will be a section mentioning your keys where you can copy your nsec. For instance, in Primal go to Settings > Keys > Copy private key, and on Amethyst open the side panel by tapping on your profile picture in the top-left, then Backup Keys > Copy my secret key.
After pasting your nsec into Amber, tap "Next."
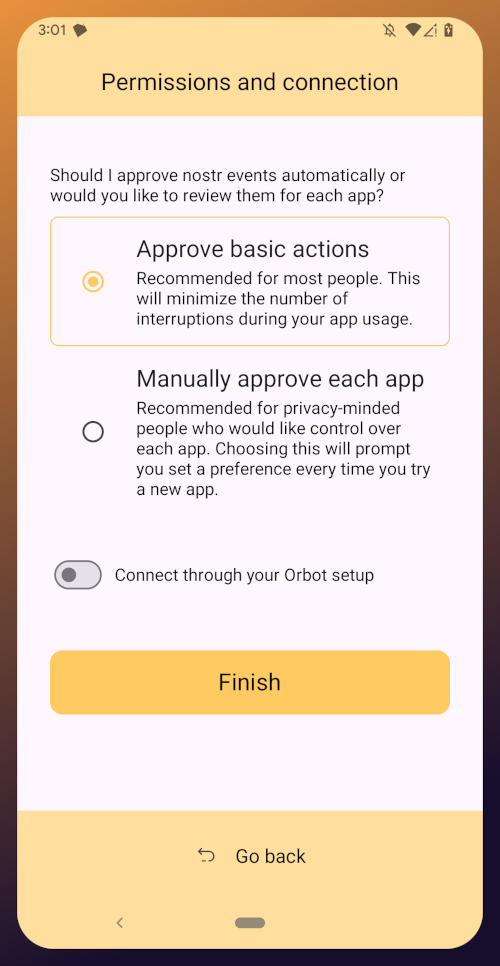
Amber will give you a couple options for a default signing policy. The default is to approve basic actions, referring to things that are common for Nostr clients to request a signature for, like following another user, liking a post, making a new post, or replying. If you are more concerned about what Amber might be signing for on your behalf, you can tell it to require manual approval for each app.
Once you've made your decision, tap "Finish." You will also be able to change this selection in the app settings at any time.
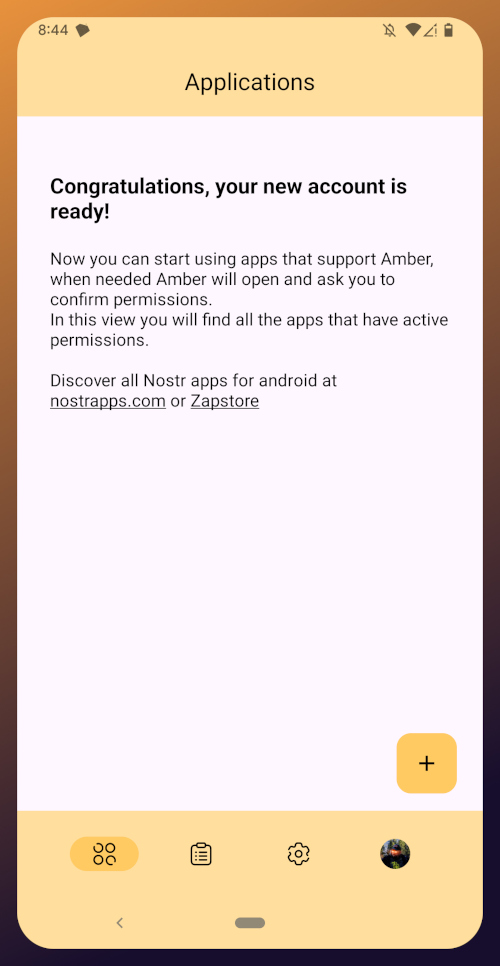
With this setup out of the way, you are now presented with the main "Applications" page of the app. You have nothing here yet, since you haven't used Amber to log into any Nostr apps, but this will be where all of the apps you have connected with Amber will be listed, in the order of the most recently used at the top.
Before we go and use Amber to log into an app, though, let's make sure we've created a backup of our private key. You pasted your nsec into Amber, so you could just save that somewhere safe, but Amber gives you a few other options as well. To find them, you'll need to tap the cog icon at the bottom of the screen to access the settings, then select "Backup Keys."
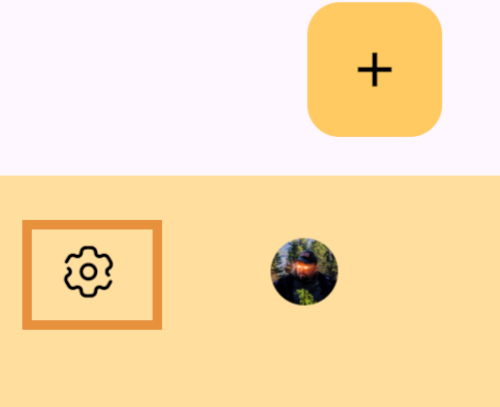
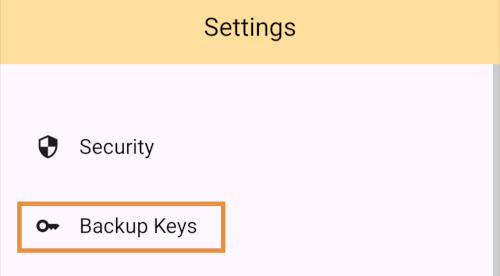
Backing Up Your Identity
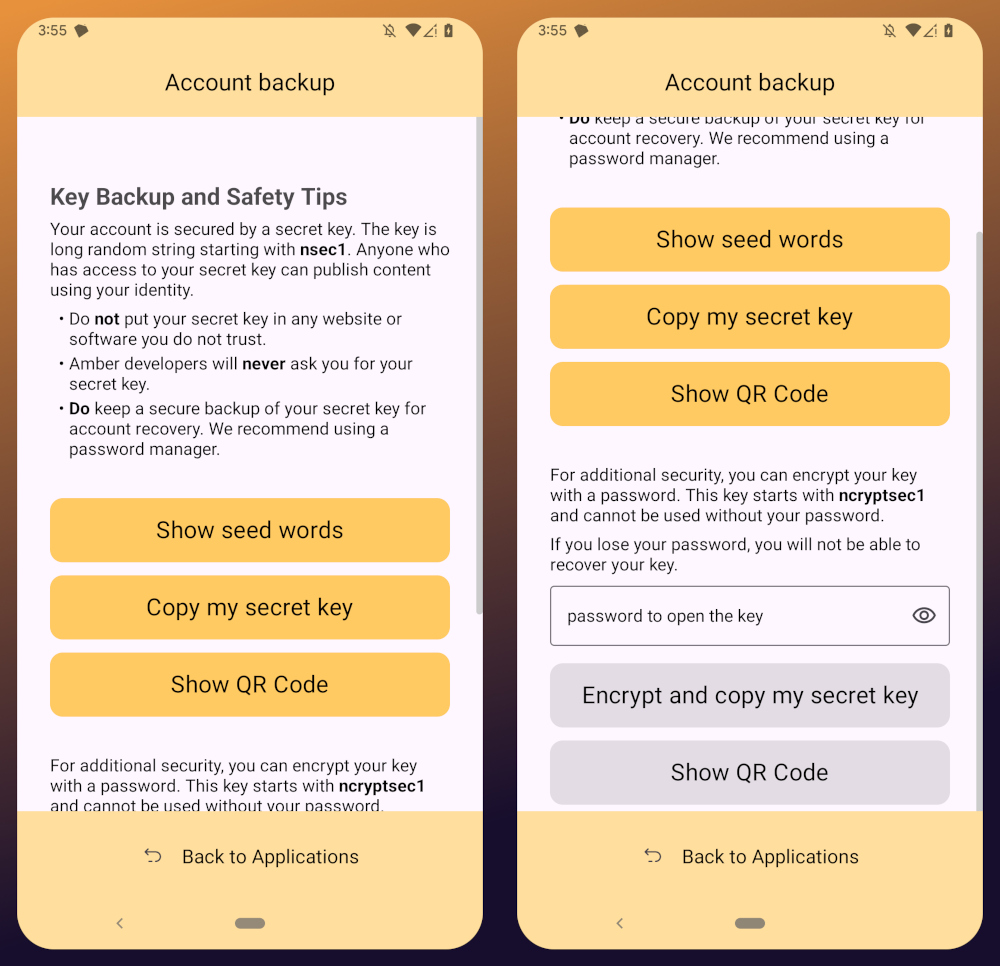
You'll notice that Amber has a few different options for backing up your private key that it can generate.
First, it can give you seed words, just like a Bitcoin seed. If you choose that option, you'll be presented with 12 words you can record somewhere safe. To recover your Nostr private key, you just have to type those words into a compatible application, such as Amber.
The next option is to just copy the secret/private key in its standard form as an "nsec." This is the least secure way to store it, but is also the most convenient, since it is simple to paste into another signer application. If you want to be able to log in on a desktop web app, the browser extension Nostr signers won't necessarily support entering your 12 word seed phrase, but they absolutely will support pasting in your nsec.
You can also display a QR code of your private key. This can be scanned by Amber signer on another device for easily transferring your private key to other devices you want to use it on. Say you have an Android tablet in addition to your phone, for instance. Just make sure you only use this function where you can be certain that no one will be able to get a photograph of that QR code. Once someone else has your nsec, there is no way to recover it. You have to start all over on Nostr. Not a big deal at this point in your journey if you just created a Nostr account, but if you have been using Nostr for a while and have built up a decent amount of reputation, it could be much more costly to start over again.
The next options are a bit more secure, because they require a password that will be used to encrypt your private key. This has some distinct advantages, and a couple disadvantages to be aware of. Using a password to encrypt your private key will give you what is called an ncryptsec, and if this is leaked somehow, whoever has it will not necessarily have access to post as you on Nostr, the way they would if your nsec had been leaked. At least, not so long as they don't also have your password. This means you can store your ncryptsec in multiple locations without much fear that it will be compromised, so long as the password you used to encrypt it was a strong and unique one, and it isn't stored in the same location. Some Nostr apps support an ncryptsec for login directly, meaning that you have the option to paste in your ncryptsec and then just log in with the password you used to encrypt it from there on out. However, now you will need to keep track of both your ncryptsec and your password, storing both of them safely and separately. Additionally, most Nostr clients and signer applications do not support using an ncryptsec, so you will need to convert it back to a standard nsec (or copy the nsec from Amber) to use those apps.
The QR option using an ncryptsec is actually quite useful, though, and I would go this route when trying to set up Amber on additional devices, since anyone possibly getting a picture of the QR code is still not going to be able to do anything with it, unless they also get the password you used to encrypt it.
All of the above options will require you to enter the PIN you set up for your device, or biometric authentication, just as an additional precaution before displaying your private key to you.
As for what "store it in a safe place" looks like, I highly recommend a self-hosted password manager, such as Vaultwarden+Bitwarden or KeePass. If you really want to get wild, you can store it on a hardware signing device, or on a steel seed plate.
Additional Settings
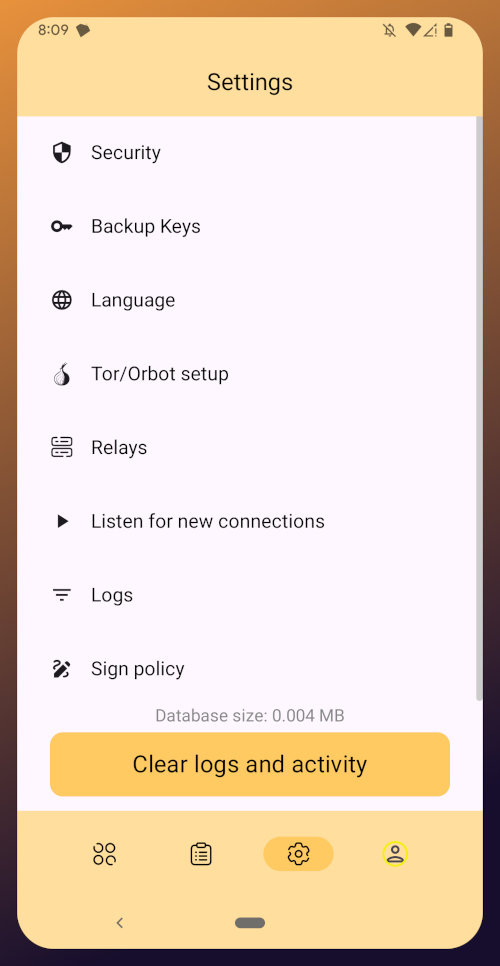
Amber has some additional settings you may want to take advantage of. First off, if you don't want just anyone who has access to your phone to be able to approve signing requests, you can go into the Security settings add a PIN or enable biometrics for signing requests. If you enable the PIN, it will be separate from the PIN you use to access your phone, so you can let someone else use your phone, like your child who is always begging to play a mobile game you have installed, without worrying that they might have access to your Nostr key to post on Amethyst.
Amber also has some relay settings. First are the "Active relays" which are used for signing requests sent to Amber remotely from Nostr web apps. This is what enables you to use Amber on your phone to log into Nostr applications on your desktop web browser, such as Jumble.social, Coracle.social, or Nostrudel.ninja, eliminating your need to use any other application to store your nsec whatsoever. You can leave this relay as the default, or you can add other relays you want to use for signing requests. Just be aware, not all relays will accept the notes that are used for Nostr signing requests, so make sure that the relay you want to use does so. In fact, Amber will make sure of this for you when you type in the relay address.
The next type of relays that you can configure in Amber are the "Default profile relays." These are used for reading your profile information. If you already had a Nostr identity that you imported to Amber, you probably noticed it loaded your profile picture and display name, setting the latter as your nickname in Amber. These relays are where Amber got that information from. The defaults are relay.nostr.band and purplepag.es. The reason for this is because they are aggregators that look for Nostr profiles that have been saved to other relays on the network and pull them in. Therefore, no matter what other relay you may save your profile to, Amber will likely be able to find it on one of those two relays as well. If you have a relay you know you will be saving your Nostr profiles to, you may want to add it to this list.
You can also set up Amber to be paired with Orbot for signing over Tor using relays that are only accessible via the Tor network. That is an advanced feature, though, and well beyond the scope of this tutorial.
Finally, you can update the default signing policy. Maybe after using Amber for a while, you've decided that the choice you made before was too strict or too lenient. You can change it to suit your needs.
Zapstore Login
Now that you are all set up with Amber, let's get you signed into your first Nostr app by going back to the Zapstore.
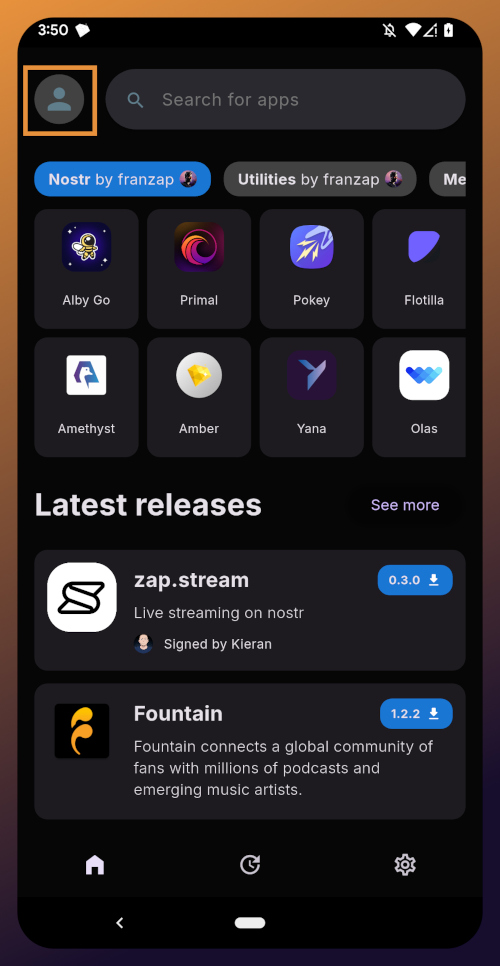
From the app's home screen, tap on the user icon in the upper left of the screen. This will open a side panel with not much on it except the option to "sign in." Go ahead and tap on it.
You will be presented with the option to either sign in with Amber, or to paste your npub. However, if you do the latter, you will only have read access, meaning you cannot zap any of the app releases. There are other features planned for the Zapstore that may also require you to be signed in with write access, so go ahead and choose to log in with Amber.
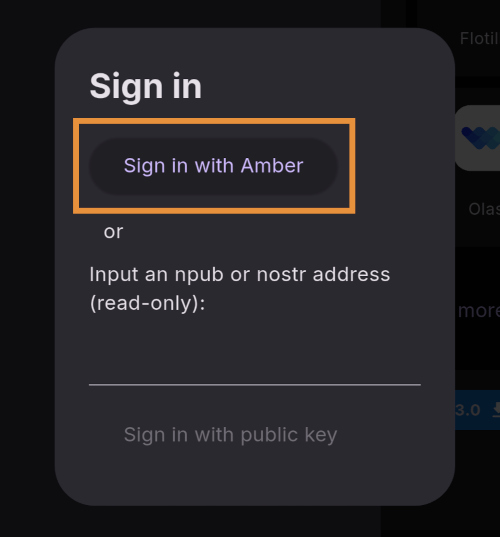
Your phone should automatically switch to Amber to approve the sign-in request.
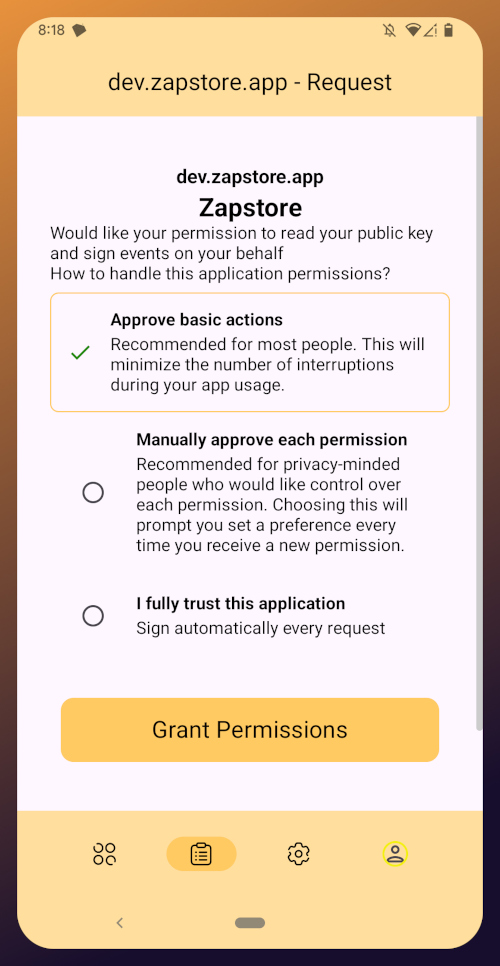
You can choose to only approve basic actions for Zapstore, require it to manually approve every time, or you can tell it that you "fully trust this application." Only choose the latter option with apps you have used for a while and they have never asked you to sign for anything suspicious. For the time being, I suggest you use the "Approve basic actions" option and tap "Grant Permissions."
Your phone will switch back to the Zapstore and will show that you are now signed in. Congratulations! From here on out, logging into most Nostr applications will be as easy as tapping on "Log in with Amber" and approving the request.
If you set up a new profile, it will just show a truncated version of your npub rather than the nickname you set up earlier. That's fine. You'll have an opportunity to update your Nostr profile in the next tutorial in this series and ensure that it is spread far and wide in the network, so the Zapstore will easily find it.
That concludes the tutorial for Amber. While we have not covered using Amber to log into Nostr web apps, that is outside the scope of this series, and I will cover it in an upcoming tutorial regarding using Amber's remote signer options in detail.
Since you're already hanging out in the Zapstore, you may as well stick around, because we will be using it right out the gate in the next part of this series: Amethyst Installation and Setup. (Coming Soon)
-
 @ c3b2802b:4850599c
2025-05-21 08:47:31
@ c3b2802b:4850599c
2025-05-21 08:47:31In einem Beitrag im Januar 2025 hatte ich das hier kurz schriftlich skizziert. Im April 2025 gab es die Gelegenheit, diese Zusammenhänge etwas ausführlicher im Café mit Katrin Huß darzustellen. Danke, liebe Katrin, für dieses Zusammenkommen in unserer Heimat Sachsen.
Wenn Sie sich für positive Psychologie und deren Einsatz beim Aufbau unserer Regionalgesellschaft interessieren, schauen Sie gern in das 45 -Minuten Gespräch!
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ e6817453:b0ac3c39
2024-12-07 14:52:47
@ e6817453:b0ac3c39
2024-12-07 14:52:47The temporal semantics and temporal and time-aware knowledge graphs. We have different memory models for artificial intelligence agents. We all try to mimic somehow how the brain works, or at least how the declarative memory of the brain works. We have the split of episodic memory and semantic memory. And we also have a lot of theories, right?
Declarative Memory of the Human Brain
How is the semantic memory formed? We all know that our brain stores semantic memory quite close to the concept we have with the personal knowledge graphs, that it’s connected entities. They form a connection with each other and all those things. So far, so good. And actually, then we have a lot of concepts, how the episodic memory and our experiences gets transmitted to the semantic:
- hippocampus indexing and retrieval
- sanitization of episodic memories
- episodic-semantic shift theory
They all give a different perspective on how different parts of declarative memory cooperate.
We know that episodic memories get semanticized over time. You have semantic knowledge without the notion of time, and probably, your episodic memory is just decayed.
But, you know, it’s still an open question:
do we want to mimic an AI agent’s memory as a human brain memory, or do we want to create something different?
It’s an open question to which we have no good answer. And if you go to the theory of neuroscience and check how episodic and semantic memory interfere, you will still find a lot of theories, yeah?
Some of them say that you have the hippocampus that keeps the indexes of the memory. Some others will say that you semantic the episodic memory. Some others say that you have some separate process that digests the episodic and experience to the semantics. But all of them agree on the plan that it’s operationally two separate areas of memories and even two separate regions of brain, and the semantic, it’s more, let’s say, protected.
So it’s harder to forget the semantical facts than the episodes and everything. And what I’m thinking about for a long time, it’s this, you know, the semantic memory.
Temporal Semantics
It’s memory about the facts, but you somehow mix the time information with the semantics. I already described a lot of things, including how we could combine time with knowledge graphs and how people do it.
There are multiple ways we could persist such information, but we all hit the wall because the complexity of time and the semantics of time are highly complex concepts.
Time in a Semantic context is not a timestamp.
What I mean is that when you have a fact, and you just mentioned that I was there at this particular moment, like, I don’t know, 15:40 on Monday, it’s already awake because we don’t know which Monday, right? So you need to give the exact date, but usually, you do not have experiences like that.
You do not record your memories like that, except you do the journaling and all of the things. So, usually, you have no direct time references. What I mean is that you could say that I was there and it was some event, blah, blah, blah.
Somehow, we form a chain of events that connect with each other and maybe will be connected to some period of time if we are lucky enough. This means that we could not easily represent temporal-aware information as just a timestamp or validity and all of the things.
For sure, the validity of the knowledge graphs (simple quintuple with start and end dates)is a big topic, and it could solve a lot of things. It could solve a lot of the time cases. It’s super simple because you give the end and start dates, and you are done, but it does not answer facts that have a relative time or time information in facts . It could solve many use cases but struggle with facts in an indirect temporal context. I like the simplicity of this idea. But the problem of this approach that in most cases, we simply don’t have these timestamps. We don’t have the timestamp where this information starts and ends. And it’s not modeling many events in our life, especially if you have the processes or ongoing activities or recurrent events.
I’m more about thinking about the time of semantics, where you have a time model as a hybrid clock or some global clock that does the partial ordering of the events. It’s mean that you have the chain of the experiences and you have the chain of the facts that have the different time contexts.
We could deduct the time from this chain of the events. But it’s a big, big topic for the research. But what I want to achieve, actually, it’s not separation on episodic and semantic memory. It’s having something in between.
Blockchain of connected events and facts
I call it temporal-aware semantics or time-aware knowledge graphs, where we could encode the semantic fact together with the time component.I doubt that time should be the simple timestamp or the region of the two timestamps. For me, it is more a chain for facts that have a partial order and form a blockchain like a database or a partially ordered Acyclic graph of facts that are temporally connected. We could have some notion of time that is understandable to the agent and a model that allows us to order the events and focus on what the agent knows and how to order this time knowledge and create the chains of the events.
Time anchors
We may have a particular time in the chain that allows us to arrange a more concrete time for the rest of the events. But it’s still an open topic for research. The temporal semantics gets split into a couple of domains. One domain is how to add time to the knowledge graphs. We already have many different solutions. I described them in my previous articles.
Another domain is the agent's memory and how the memory of the artificial intelligence treats the time. This one, it’s much more complex. Because here, we could not operate with the simple timestamps. We need to have the representation of time that are understandable by model and understandable by the agent that will work with this model. And this one, it’s way bigger topic for the research.”

